-
 @ 266815e0:6cd408a5
2024-04-22 22:20:47
@ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent
I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS
There were a few things I learned from all these conversations:
- All the existing solutions have one thing in common. A universal ID of some kind for files
- HTTP is still good. we don't have to throw the baby out with the bath water
- nostr could fix this... somehow
Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing...
An Identity system
An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files
This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends)
What is blossom?
Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id
What are Blobs?
blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names
Instead blobs have a sha256 hash (like
b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553) as an IDThese IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using:
sha256sum bitcoin.pdf)How do the servers work?
Blossom servers expose four endpoints to let clients and users upload and manage blobs
GET /<sha256>(optional file.ext)PUT /uploadAuthentication: Signed nostr event- Returns a blob descriptor
GET /list/<pubkey>- Returns an array of blob descriptors
Authentication(optional): Signed nostr eventDELETE /<sha256>Authentication: Signed nostr event
What is Blossom Drive?
Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs
What are Drives
Drives are just nostr events (kind
30563) that store a map of blobs and what filename they should have along with some extra metadataAn example drive event would be
json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] }There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at
If your interested, the full event definition is at github.com/hzrd149/blossom-drive
Getting started
Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started
1. Open the app
Open https://blossom.hzrd149.com
2. Login using extension

You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an
ncryptsecpassword protected private key - ansecunprotected private key (please don't) - bunker:// URI from nsecbunker3. Add a blossom server

Right now
https://cdn.satellite.earthis the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript github.com/hzrd149/blossom-server4. Start uploading your files
NOTE: All files upload to blossom drive are public by default. DO NOT upload private files

5. Manage files

Encrypted drives
There is also the option to encrypt drives using NIP-49 password encryption. although its not tested at all so don't trust it, verify

Whats next?
I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything
also all the images in this article are stored in one of my blossom drives here
nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
-
 @ f977c464:32fcbe00
2024-01-30 20:06:18
@ f977c464:32fcbe00
2024-01-30 20:06:18Güneşin kaybolmasının üçüncü günü, saat öğlen on ikiyi yirmi geçiyordu. Trenin kalkmasına yaklaşık iki saat vardı. Hepimiz perondaydık. Valizlerimiz, kolilerimiz, renk renk ve biçimsiz çantalarımızla yan yana dizilmiş, kısa aralıklarla tepemizdeki devasa saati kontrol ediyorduk.
Ama ne kadar dik bakarsak bakalım zaman bir türlü istediğimiz hızla ilerlemiyordu. Herkes birkaç dakika sürmesi gereken alelade bir doğa olayına sıkışıp kalmış, karanlıktan sürünerek çıkmayı deniyordu.
Bekleme salonuna doğru döndüm. Nefesimden çıkan buharın arkasında, kalın taş duvarları ve camlarıyla morg kadar güvenli ve soğuk duruyordu. Cesetleri o yüzden bunun gibi yerlere taşımaya başlamışlardı. Demek insanların bütün iyiliği başkaları onları gördüğü içindi ki gündüzleri gecelerden daha karanlık olduğunda hemen birbirlerinin gırtlağına çökmüş, böğürlerinde delikler açmış, gözlerini oyup kafataslarını parçalamışlardı.
İstasyonun ışığı titrediğinde karanlığın enseme saplandığını hissettim. Eğer şimdi, böyle kalabalık bir yerde elektrik kesilse başımıza ne gelirdi?
İçerideki askerlerden biri bakışlarımı yakalayınca yeniden saate odaklanmış gibi yaptım. Sadece birkaç dakika geçmişti.
“Tarlalarım gitti. Böyle boyum kadar ayçiçeği doluydu. Ah, hepsi ölüp gidiyor. Afitap’ın çiçekleri de gi-”
“Dayı, Allah’ını seversen sus. Hepimizi yakacaksın şimdi.”
Karanlıkta durduğunda, görünmez olmayı istemeye başlıyordun. Kimse seni görmemeli, nefesini bile duymamalıydı. Kimsenin de ayağının altında dolaşmamalıydın; gelip kazayla sana çarpmamalılar, takılıp sendelememeliydiler. Yoksa aslında hedefi sen olmadığın bir öfke gürlemeye başlar, yaşadığın ilk şoku ve acıyı silerek üstünden geçerdi.
İlk konuşan, yaşlıca bir adam, kafasında kasketi, nasırlı ellerine hohluyordu. Gözleri ve burnu kızarmıştı. Güneşin kaybolması onun için kendi başına bir felaket değildi. Hayatına olan pratik yansımalarından korkuyordu olsa olsa. Bir anının kaybolması, bu yüzden çoktan kaybettiği birinin biraz daha eksilmesi. Hayatta kalmasını gerektiren sebepler azalırken, hayatta kalmasını sağlayacak kaynaklarını da kaybediyordu.
Onu susturan delikanlıysa atkısını bütün kafasına sarmış, sakalı ve yüzünün derinliklerine kaçmış gözleri dışında bedeninin bütün parçalarını gizlemeye çalışıyordu. İşte o, güneşin kaybolmasının tam olarak ne anlama geldiğini anlamamış olsa bile, dehşetini olduğu gibi hissedebilenlerdendi.
Güneşin onlardan alındıktan sonra kime verileceğini sormuyorlardı. En başta onlara verildiğinde de hiçbir soru sormamışlardı zaten.
İki saat ne zaman geçer?
Midemin üstünde, sağ tarafıma doğru keskin bir acı hissettim. Karaciğerim. Gözlerimi yumdum. Yanımda biri metal bir nesneyi yere bıraktı. Bir kafesti. İçerisindeki kartalın ıslak kokusu burnuma ulaşmadan önce bile biliyordum bunu.
“Yeniden mi?” diye sordu bana kartal. Kanatları kanlı. Zamanın her bir parçası tüylerinin üstüne çöreklenmişti. Gagası bir şey, tahminen et parçası geveliyor gibi hareket ediyordu. Eski anılar kolay unutulmazmış. Şu anda kafesinin kalın parmaklıklarının ardında olsa da bunun bir aldatmaca olduğunu bir tek ben biliyordum. Her an kanatlarını iki yana uzatıverebilir, hava bu hareketiyle dalgalanarak kafesi esneterek hepimizi içine alacak kadar genişleyebilir, parmaklıklar önce ayaklarımızın altına serilir gibi gözükebilir ama aslında hepimizin üstünde yükselerek tepemize çökebilirdi.
Aşağıya baktım. Tahtalarla zapt edilmiş, hiçbir yere gidemeyen ama her yere uzanan tren rayları. Atlayıp koşsam… Çantam çok ağırdı. Daha birkaç adım atamadan, kartal, suratını bedenime gömerdi.
“Bu sefer farklı,” diye yanıtladım onu. “Yeniden diyemezsin. Tekrarladığım bir şey değil bu. Hatta bir hata yapıyormuşum gibi tonlayamazsın da. Bu sefer, insanların hak etmediğini biliyorum.”
“O zaman daha vahim. Süzme salaksın demektir.”
“İnsanların hak etmemesi, insanlığın hak etmediği anlamına gelmez ki.”
Az önce göz göze geldiğim genççe ama çökük asker hâlâ bana bakıyordu. Bir kartalla konuştuğumu anlamamıştı şüphesiz. Yanımdakilerden biriyle konuştuğumu sanmış olmalıydı. Ama konuştuğum kişiye bakmıyordum ona göre. Çekingence kafamı eğmiştim. Bir kez daha göz göze geldiğimizde içerideki diğer iki askere bir şeyler söyledi, onlar dönüp beni süzerken dışarı çıktı.
Yanımızdaki, az önce konuşan iki adam da şaşkınlıkla bir bana bir kartala bakıyordu.
“Yalnız bu sefer kalbin de kırılacak, Prometheus,” dedi kartal, bana. “Belki son olur. Biliyorsun, bir sürü soruna neden oluyor bu yaptıkların.”
Beni koruyordu sözde. En çok kanıma dokunan buydu. Kasıklarımın üstüne oturmuş, kanlı suratının ardında gözleri parlarken attığı çığlık kulaklarımda titremeye devam ediyordu. Bu tabloda kimsenin kimseyi düşündüğü yoktu. Kartalın, yanımızdaki adamların, artık arkama kadar gelmiş olması gereken askerin, tren raylarının, geçmeyen saatlerin…
Arkamı döndüğümde, asker sahiden oradaydı. Zaten öyle olması gerekiyordu; görmüştüm bunu, biliyordum. Kehanetler… Bir şeyler söylüyordu ama ağzı oynarken sesi çıkmıyordu. Yavaşlamış, kendisini saatin akışına uydurmuştu. Havada donan tükürüğünden anlaşılıyordu, sinirliydi. Korktuğu için olduğunu biliyordum. Her seferinde korkmuşlardı. Beni unutmuş olmaları işlerini kolaylaştırmıyordu. Sadece yeni bir isim vermelerine neden oluyordu. Bu seferkiyle beni lanetleyecekleri kesinleşmişti.
Olması gerekenle olanların farklı olması ne kadar acınasıydı. Olması gerekenlerin doğasının kötücül olmasıysa bir yerde buna dayanıyordu.
“Salaksın,” dedi kartal bana. Zamanı aşan bir çığlık. Hepimizin önüne geçmişti ama kimseyi durduramıyordu.
Sonsuzluğa kaç tane iki saat sıkıştırabilirsiniz?
Ben bir tane bile sıkıştıramadım.
Çantama uzanıyordum. Asker de sırtındaki tüfeğini indiriyordu. Benim acelem yoktu, onunsa eli ayağı birbirine dolaşıyordu. Oysaki her şey tam olması gerektiği anda olacaktı. Kehanet başkasının parmaklarının ucundaydı.
Güneş, bir tüfeğin patlamasıyla yeryüzüne doğdu.
Rayların üzerine serilmiş göğsümün ortasından, bir çantanın içinden.
Not: Bu öykü ilk olarak 2021 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28O Planetinha
Fumaça verde me entrando pelas narinas e um coro desafinado fazia uma base melódica.
nos confins da galáxia havia um planetinha isolado. Era um planeta feliz.
O homem vestido de mago começava a aparecer por detrás da fumaça verde.
O planetinha recebeu três presentes, mas o seu habitante, o homem, estava num estado de confusão tão grande que ameaçava estragá-los. Os homens já havia escravizado o primeiro presente, a vida; lutavam contra o segundo presente, a morte; e havia alguns que achavam que deviam destruir totalmente o terceiro, o amor, e com isto levar a desordem total ao pobre planetinha perdido, que se chamava Terra.
O coro desafinado entrou antes do "Terra" cantando várias vezes, como se imitasse um eco, "terra-terra-terraaa". Depois de uma pausa dramática, o homem vestido de mago voltou a falar.
Terra, nossa nave mãe.
Neste momento eu me afastei. À frente do palco onde o mago e seu coral faziam apelos à multidão havia vários estandes cobertos com a tradicional armação de quatro pernas e lona branca. Em todos os cantos da praça havia gente, gente dos mais variados tipos. Visitantes curiosos que se aproximavam atraídos pela fumaça verde e as barraquinhas, gente que aproveitava o movimento para vender doces sem pagar imposto, casais que se abraçavam de pé para espantar o frio, os tradicionais corredores que faziam seu cooper, gente cheia de barba e vestida para imitar os hippies dos anos 60 e vender colares estendidos no chão, transeuntes novos e velhos, vestidos como baladeiros ou como ativistas do ônibus grátis, grupos de ciclistas entusiastas.
O mago fazia agora apelos para que nós, os homens, habitantes do isolado planetinha, passássemos a ver o planetinha, nossa nave mãe, como um todo, e adquiríssemos a consciência de que ele estava entrando em maus lençóis. A idéia, reforçada pela logomarca do evento, era que parássemos de olhar só para a nossa vida e pensássemos no planeta.
A logomarca do evento, um desenho estilizado do planeta Terra, nada tinha a ver com seu nome: "Festival Andando de Bem com a Vida", mas havia sido ali colocada estrategicamente pelos organizadores, de quem parecia justamente sair a mensagem dita pelo mago.
Aquela multidão de pessoas que, assim como eu, tinham suas próprias preocupações, não podiam ver o quadro caótico que formavam, cada uma com seus atos isolados, ali naquela praça isolada, naquele planeta isolado. Quando o hippie barbudo, quase um Osho, assustava um casal para tentar vender-lhes um colar, a quantidade de caos que isto acrescentava à cena era gigantesca. Por um segundo, pude ver, como se estivesse de longe e acima, com toda a pretensão que este estado imaginativo carrega, a cena completa do caos.
Uma nave-mãe, dessas de ficção científica, habitada por milhões de pessoas, seguia no espaço sem rumo, e sem saber que logo à frente um longo precipício espacial a esperava, para a desgraça completa sua e de seus habitantes.
Acostumados àquela nave tanto quanto outrora estiveram acostumados à sua terra natal, os homens viviam as próprias vidas sem nem se lembrar que estavam vagando pelo espaço. Ninguém sabia quem estava conduzindo a nave, e ninguém se importava.
No final do filme descobre-se que era a soma completa do caos que cada habitante produzia, com seus gestos egoístas e incapazes de levar em conta a totalidade, é que determinava a direção da nave-mãe. O efeito, no entanto, não era imediato, como nunca é. Havia gente de verdade encarregada de conduzir a nave, mas era uma gente bêbada, mau-caráter, que vivia brigando pelo controle da nave e o poder que isto lhes dava. Poder, status, dinheiro!
Essa gente bêbada era atraída até ali pela corrupção das instituições e da moral comum que, no fundo no fundo, era causada pelo egoísmo da população, através de um complexo -- mas que no filme aparece simplificado pela ação individual de um magnata do divertimento público -- processo social.
O homem vestido de mago era mais um agente causador de caos, com sua cena cheia de fumaça e sua roupa estroboscópica, ele achava que estava fazendo o bem ao alertar sua platéia, todos as sextas-feiras, de que havia algo que precisava ser feito, que cada um que estava ali ouvindo era responsável pelo planeta. A sua incapacidade, porém, de explicar o que precisava ser feito só aumentava a angústia geral; a culpa que ele jogava sobre seu público, e que era prontamente aceita e passada em frente, aos familiares e amigos de cada um, atormentava-os diariamente e os impedia de ter uma vida decente no trabalho e em casa. As famílias, estressadas, estavam constantemente brigando e os motivos mais insignificantes eram responsáveis pelas mais horrendas conseqüências.
O mago, que após o show tirava o chapéu entortado e ia tomar cerveja num boteco, era responsável por uma parcela considerável do caos que levava a nave na direção do seu desgraçado fim. No filme, porém, um dos transeuntes que de passagem ouviu um pedaço do discurso do mago despertou em si mesmo uma consiência transformadora e, com poderes sobre-humanos que lhe foram então concedidos por uma ordem iniciática do bem ou não, usando só os seus poderes humanos mesmo, o transeunte -- na primeira versão do filme um homem, na segunda uma mulher -- consegue consertar as instituições e retirar os bêbados da condução da máquina. A questão da moral pública é ignorada para abreviar a trama, já com duas horas e quarenta de duração, mas subentende-se que ela também fora resolvida.
No planeta Terra real, que não está indo em direção alguma, preso pela gravidade ao Sol, e onde as pessoas vivem a própria vida porque lhes é impossível viver a dos outros, não têm uma consciência global de nada porque só é possível mesmo ter a consciência delas mesmas, e onde a maioria, de uma maneira ou de outra, está tentando como pode, fazer as coisas direito, o filme é exibido.
Para a maioria dos espectadores, é um filme que evoca reflexões, um filme forte. Por um segundo elas têm o mesmo vislumbre do caos generalizado que eu tive ali naquela praça. Para uma pequena parcela dos espectadores -- entre eles alguns dos que estavam na platéia do mago, o próprio mago, o seguidor do Osho, o casal de duas mulheres e o vendedor de brigadeiros, mas aos quais se somam também críticos de televisão e jornal e gente que fala pelos cotovelos na internet -- o filme é um horror, o filme é uma vulgarização de um problema real e sério, o filme apela para a figura do herói salvador e passa uma mensagem totalmente errada, de que a maioria da população pode continuar vivendo as suas própria vidinhas miseráveis enquanto espera por um herói que vem do Olimpo e os salva da mixórdia que eles mesmos causaram, é um filme que presta um enorme desserviço à causa.
No dia seguinte ao lançamento, num bar meio caro ali perto da praça, numa mesa com oito pessoas, entre elas seis do primeiro grupo e oito do segundo, discute-se se o filme levará ou não o Oscar. Eu estou em casa dormindo e não escuto nada.
-
 @ ad3225f6:28a2f9a2
2024-04-22 15:53:30
@ ad3225f6:28a2f9a2
2024-04-22 15:53:30What is the one book that you have given out as a gift the most or alternatively the one book you read in the past year that has positively impacted your life the most?
-
 @ f977c464:32fcbe00
2024-01-11 18:47:47
@ f977c464:32fcbe00
2024-01-11 18:47:47Kendisini aynada ilk defa gördüğü o gün, diğerleri gibi olduğunu anlamıştı. Oysaki her insan biricik olmalıydı. Sözgelimi sinirlendiğinde bir kaşı diğerinden birkaç milimetre daha az çatılabilirdi veya sevindiğinde dudağı ona has bir açıyla dalgalanabilirdi. Hatta bunların hiçbiri mümkün değilse, en azından, gözlerinin içinde sadece onun sahip olabileceği bir ışık parlayabilirdi. Çok sıradan, öyle sıradan ki kimsenin fark etmediği o milyonlarca minik şeyden herhangi biri. Ne olursa.
Ama yansımasına bakarken bunların hiçbirini bulamadı ve diğer günlerden hiç de farklı başlamamış o gün, işe gitmek için vagonunun gelmesini beklediği alelade bir metro istasyonunda, içinde kaybolduğu illüzyon dağılmaya başladı.
İlk önce derisi döküldü. Tam olarak dökülmedi aslında, daha çok kıvılcımlara dönüşüp bedeninden fırlamış ve bir an sonra sönerek külleşmiş, havada dağılmıştı. Ardında da, kaybolmadan hemen önce, kısa süre için hayal meyal görülebilen, bir ruhun yok oluşuna ağıt yakan rengârenk peri cesetleri bırakmıştı. Beklenenin aksine, havaya toz kokusu yayıldı.
Dehşete düştü elbette. Dehşete düştüler. Panikle üstlerini yırtan 50 işçi. Her şeyin sebebiyse o vagon.
Saçları da döküldü. Her tel, yere varmadan önce, her santimde ikiye ayrıla ayrıla yok oldu.
Bütün yüzeylerin mat olduğu, hiçbir şeyin yansımadığı, suyun siyah aktığı ve kendine ancak kameralarla bakabildiğin bir dünyada, vagonun içine yerleştirilmiş bir aynadan ilk defa kendini görmek.
Gözlerinin akları buharlaşıp havada dağıldı, mercekleri boşalan yeri doldurmak için eriyip yayıldı. Gerçeği görmemek için yaratılmış, bu yüzden görmeye hazır olmayan ve hiç olmayacak gözler.
Her şeyin o anda sona erdiğini sanabilirdi insan. Derin bir karanlık ve ölüm. Görmenin görmek olduğu o anın bitişi.
Ben geldiğimde ölmüşlerdi.
Yani bozulmuşlardı demek istiyorum.
Belleklerini yeni taşıyıcılara takmam mümkün olmadı. Fiziksel olarak kusursuz durumdaydılar, olmayanları da tamir edebilirdim ama tüm o hengamede kendilerini baştan programlamış ve girdilerini modifiye etmişlerdi.
Belleklerden birini masanın üzerinden ileriye savurdu. Hınca hınç dolu bir barda oturuyorlardı. O ve arkadaşı.
Sırf şu kendisini insan sanan androidler travma geçirip delirmesin diye neler yapıyoruz, insanın aklı almıyor.
Eliyle arkasını işaret etti.
Polislerin söylediğine göre biri vagonun içerisine ayna yerleştirmiş. Bu zavallılar da kapı açılıp bir anda yansımalarını görünce kafayı kırmışlar.
Arkadaşı bunların ona ne hissettirdiğini sordu. Yani o kadar bozuk, insan olduğunu sanan androidi kendilerini parçalamış olarak yerde görmek onu sarsmamış mıydı?
Hayır, sonuçta belirli bir amaç için yaratılmış şeyler onlar. Kaliteli bir bilgisayarım bozulduğunda üzülürüm çünkü parasını ben vermişimdir. Bunlarsa devletin. Bana ne ki?
Arkadaşı anlayışla kafasını sallayıp suyundan bir yudum aldı. Kravatını biraz gevşetti.
Bira istemediğinden emin misin?
İstemediğini söyledi. Sahi, neden deliriyordu bu androidler?
Basit. Onların yapay zekâlarını kodlarken bir şeyler yazıyorlar. Yazılımcılar. Biliyorsun, ben donanımdayım. Bunlar da kendilerini insan sanıyorlar. Tiplerine bak.
Sesini alçalttı.
Arabalarda kaza testi yapılan mankenlere benziyor hepsi. Ağızları burunları bile yok ama şu geldiğimizden beri sakalını düzeltip duruyor mesela. Hayır, hepsi de diğerleri onun sakalı varmış sanıyor, o manyak bir şey.
Arkadaşı bunun delirmeleriyle bağlantısını çözemediğini söyledi. O da normal sesiyle konuşmaya devam etti.
Anlasana, aynayı falan ayırt edemiyor mercekleri. Lönk diye kendilerini görüyorlar. Böyle, olduğu gibi...
Nedenmiş peki? Ne gerek varmış?
Ne bileyim be abicim! Ahiret soruları gibi.
Birasına bakarak dalıp gitti. Sonra masaya abanarak arkadaşına iyice yaklaştı. Bulanık, bir tünelin ucundaki biri gibi, şekli şemalı belirsiz bir adam.
Ben seni nereden tanıyorum ki ulan? Kimsin sen?
Belleği makineden çıkardılar. İki kişiydiler. Soruşturmadan sorumlu memurlar.
─ Baştan mı başlıyoruz, diye sordu belleği elinde tutan ilk memur.
─ Bir kere daha deneyelim ama bu sefer direkt aynayı sorarak başla, diye cevapladı ikinci memur.
─ Bence de. Yeterince düzgün çalışıyor.
Simülasyon yüklenirken, ayakta, biraz arkada duran ve alnını kaşıyan ikinci memur sormaktan kendisini alamadı:
─ Bu androidleri niye böyle bir olay yerine göndermişler ki? Belli tost olacakları. İsraf. Gidip biz baksak aynayı kırıp delilleri mahvetmek zorunda da kalmazlar.
Diğer memur sandalyesinde hafifçe dönecek oldu, o sırada soruyu bilgisayarın hoparlöründen teknisyen cevapladı.
Hangi işimizde bir yamukluk yok ki be abi.
Ama bir son değildi. Üstlerindeki tüm illüzyon dağıldığında ve çıplak, cinsiyetsiz, birbirinin aynı bedenleriyle kaldıklarında sıra dünyaya gelmişti.
Yere düştüler. Elleri -bütün bedeni gibi siyah turmalinden, boğumları çelikten- yere değdiği anda, metronun zemini dağıldı.
Yerdeki karolar öncesinde beyazdı ve çok parlaktı. Tepelerindeki floresan, ışığını olduğu gibi yansıtıyor, tek bir lekenin olmadığı ve tek bir tozun uçmadığı istasyonu aydınlatıyorlardı.
Duvarlara duyurular asılmıştı. Örneğin, yarın akşam kültür merkezinde 20.00’da başlayacak bir tekno blues festivalinin cıvıl cıvıl afişi vardı. Onun yanında daha geniş, sarı puntolu harflerle yazılmış, yatay siyah kesiklerle çerçevesi çizilmiş, bir platformdan düşen çöp adamın bulunduğu “Dikkat! Sarı bandı geçmeyin!” uyarısı. Biraz ilerisinde günlük resmi gazete, onun ilerisinde bir aksiyon filminin ve başka bir romantik komedi filminin afişleri, yapılacakların ve yapılmayacakların söylendiği küçük puntolu çeşitli duyurular... Duvar uzayıp giden bir panoydu. On, on beş metrede bir tekrarlanıyordu.
Tüm istasyonun eni yüz metre kadar. Genişliği on metre civarı.
Önlerinde, açık kapısından o mendebur aynanın gözüktüğü vagon duruyordu. Metro, istasyona sığmayacak kadar uzundu. Bir kılıcın keskinliğiyle uzanıyor ama yer yer vagonların ek yerleriyle bölünüyordu.
Hiçbir vagonda pencere olmadığı için metronun içi, içlerindekiler meçhuldü.
Sonrasında karolar zerrelerine ayrılarak yükseldi. Floresanın ışığında her yeri toza boğdular ve ortalığı gri bir sisin altına gömdüler. Çok kısa bir an. Afişleri dalgalandırmadılar. Dalgalandırmaya vakitleri olmadı. Yerlerinden söküp aldılar en fazla. Işık birkaç kere sönüp yanarak direndi. Son kez söndüğünde bir daha geri gelmedi.
Yine de etraf aydınlıktı. Kırmızı, her yere eşit dağılan soluk bir ışıkla.
Yer tamamen tele dönüşmüştü. Altında çapraz hatlarla desteklenmiş demir bir iskelet. Işık birkaç metreden daha fazla aşağıya uzanamıyordu. Sonsuzluğa giden bir uçurum.
Duvarın yerini aynı teller ve demir iskelet almıştı. Arkasında, birbirine vidalarla tutturulmuş demir plakalardan oluşan, üstünden geçen boruların ek yerlerinden bazen ince buharların çıktığı ve bir süre asılı kaldıktan sonra ağır, yağlı bir havayla sürüklendiği bir koridor.
Diğer tarafta paslanmış, pencerelerindeki camlar kırıldığı için demir plakalarla kapatılmış külüstür bir metro. Kapının karşısındaki aynadan her şey olduğu gibi yansıyordu.
Bir konteynırın içini andıran bir evde, gerçi gayet de birbirine eklenmiş konteynırlardan oluşan bir şehirde “andıran” demek doğru olmayacağı için düpedüz bir konteynırın içinde, masaya mum görüntüsü vermek için koyulmuş, yarı katı yağ atıklarından şekillendirilmiş kütleleri yakmayı deniyordu. Kafasında hayvan kıllarından yapılmış grili siyahlı bir peruk. Aynı kıllardan kendisine gür bir bıyık da yapmıştı.
Üstünde mavi çöp poşetlerinden yapılmış, kravatlı, şık bir takım.
Masanın ayakları yerine oradan buradan çıkmış parçalar konulmuştu: bir arabanın şaft mili, üst üste konulmuş ve üstünde yazı okunamayan tenekeler, boş kitaplar, boş gazete balyaları... Hiçbir şeye yazı yazılmıyordu, gerek yoktu da zaten çünkü merkez veri bankası onları fark ettirmeden, merceklerden giren veriyi sentezleyerek insanlar için dolduruyordu. Yani, androidler için. Farklı şekilde isimlendirmek bir fark yaratacaksa.
Onların mercekleri için değil. Bağlantıları çok önceden kopmuştu.
─ Hayatım, sofra hazır, diye bağırdı yatak odasındaki karısına.
Sofrada tabak yerine düz, bardak yerine bükülmüş, çatal ve bıçak yerine sivriltilmiş plakalar.
Karısı salonun kapısında durakladı ve ancak kulaklarına kadar uzanan, kocasınınkine benzeyen, cansız, ölü hayvanların kıllarından ibaret peruğunu eliyle düzeltti. Dudağını, daha doğrusu dudağının olması gereken yeri koyu kırmızı bir yağ tabakasıyla renklendirmeyi denemişti. Biraz da yanaklarına sürmüştü.
─ Nasıl olmuş, diye sordu.
Sesi tek düzeydi ama hafif bir neşe olduğunu hissettiğinize yemin edebilirdiniz.
Üzerinde, çöp poşetlerinin içini yazısız gazete kağıtlarıyla doldurarak yaptığı iki parça giysi.
─ Çok güzelsin, diyerek kravatını düzeltti kocası.
─ Sen de öylesin, sevgilim.
Yaklaşıp kocasını öptü. Kocası da onu. Sonra nazikçe elinden tutarak, sandalyesini geriye çekerek oturmasına yardım etti.
Sofrada yemek niyetine hiçbir şey yoktu. Gerek de yoktu zaten.
Konteynırın kapısı gürültüyle tekmelenip içeri iki memur girene kadar birbirlerine öyküler anlattılar. O gün neler yaptıklarını. İşten erken çıkıp yemyeşil çimenlerde gezdiklerini, uçurtma uçurduklarını, kadının nasıl o elbiseyi bulmak için saatlerce gezip yorulduğunu, kocasının kısa süreliğine işe dönüp nasıl başarılı bir hamleyle yaşanan krizi çözdüğünü ve kadının yanına döndükten sonra, alışveriş merkezinde oturdukları yeni dondurmacının dondurmalarının ne kadar lezzetli olduğunu, boğazlarının ağrımasından korktuklarını...
Akşam film izleyebilirlerdi, televizyonda -boş ve mat bir plaka- güzel bir film oynayacaktı.
İki memur. Çıplak bedenleriyle birbirinin aynı. Ellerindeki silahları onlara doğrultmuşlardı. Mum ışığında, tertemiz bir örtünün serili olduğu masada, bardaklarında şaraplarla oturan ve henüz sofranın ortasındaki hindiye dokunmamış çifti gördüklerinde bocaladılar.
Hiç de androidlere bilinçli olarak zarar verebilecek gibi gözükmüyorlardı.
─ Sessiz kalma hakkına sahipsiniz, diye bağırdı içeri giren ikinci memur. Söylediğiniz her şey...
Cümlesini bitiremedi. Yatak odasındaki, masanın üzerinden gördüğü o şey, onunla aynı hareketleri yapan android, yoksa, bir aynadaki yansıması mıydı?
Bütün illüzyon o anda dağılmaya başladı.
Not: Bu öykü ilk olarak 2020 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ bcea2b98:7ccef3c9
2024-04-20 17:59:17
@ bcea2b98:7ccef3c9
2024-04-20 17:59:17Consider the concept of 'progress' in human society and individual lives. When we talk about progress, what exactly do we mean? Is it solely about technological advancement, economic growth, or societal development? Or does progress include broader aspects such as personal fulfillment, moral advancement, and environmental sustainability? Is progress always desirable, or are there instances where the pursuit of progress leads to unintended consequences or ethical dilemmas?
-
 @ bcea2b98:7ccef3c9
2024-04-20 00:11:30
@ bcea2b98:7ccef3c9
2024-04-20 00:11:30 -
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ 9071d94a:6967c53b
2024-04-19 18:15:50
@ 9071d94a:6967c53b
2024-04-19 18:15:50test test test
-
 @ de496884:72617b81
2023-11-20 13:54:02
@ de496884:72617b81
2023-11-20 13:54:02Hola nostriches. Hoy quiero hacer una publicación a modo de acercamiento al surgimiento de las categorías de género y feminismo. Así que si te interesa el tema haz un esfuerzo, quédate y lee hasta el final.
El «nuevo» feminismo surge en los años 60 en aquellos países desarrollados que acordaron el reconocimiento a los derechos humanos contenidos en la declaración respectiva de la ONU. Entonces, como extensión a dicho reconocimiento es que se gesta el movimiento feminista. A partir de entonces, se vuelve a plantear la relación entre naturaleza y cultura y se llega a la conclusión de que las diferencias sociales van más allá de las diferencias biológicas, lo cual tiene que ver con que hasta la satisfacción de las necesidades elementales como son la alimentación, la vivienda o el vestuario, están condicionadas por construcciones sociales.
Pues resulta que una de las primeras propuestas identificó la subordinación femenina producto de una organización patriarcal, tomando la categoría patriarcado de Max Weber. Es así como la visión de patriarcado se extendió al discurso político y académico. Sin embargo, no existía información acerca del desarrollo histórico de dicha categoría, sistematización, variaciones, etc., debido a que era algo que recién se percibía en sociedad.
Sin embargo, la misma categoría de patriarcado junto a la de relaciones de poder para explicar fenómenos sociales contemporáneos, constituye uno de los principales aportes del feminismo. Es así como han logrado primero visibilizar y luego deconstruir y desmontar una serie de patrones existentes en la cultura que hacían a la mujer subordinarse al hombre, y que estaban presentes en el sistema sexo/género.
 Imagen relativa a la lucha contra el patriarcado
Imagen relativa a la lucha contra el patriarcadoHasta ese momento, en las investigaciones de corte sociológico se podía observar un androcentrismo excesivo al dar cuenta de que el discurso científico giraba en torno al hombre como sujeto y objeto de la investigación. Incluso para muchos positivistas como el mismo Weber, los problemas relativos a las mujeres quedaban en un segundo plano y eran achacados a una supuesta pasividad en el ámbito doméstico-familiar. Dicha pasividad partía de la supuesta inferioridad biológica del género femenino.
El patriarcado entonces era una categoría vacía en sí misma, sin valor explicativo. Desde el punto de vista político pudo ser útil para la movilización pero no resistió la polémica de los críticos del feminismo ni problematizó los conflictos a ser resueltos. Pero por otro lado, un grupo de mujeres -académicas principalmente- se puso manos a la obra en una tarea más pequeña pero con mayores resultados a la larga. Se propusieron generar conocimientos sobre las condiciones de vida de la mujer, buscar en el pasado y el presente los aportes de las mujeres a la sociedad, hacerlas visibles en la historia. Es así como surgen centros académicos, ONG, proyectos, centros de estudios sobre la mujer, etc.
Convendría distinguir entonces dos posturas que acompañaron a la investigación sobre las mujeres: uno que toma como objeto de estudio a la mujer; condiciones de vida, trabajo, cultura, y otra que privilegia a la sociedad como generadora de la subordinación de las mujeres. Mientras la primera perspectiva generaba conocimiento sobre las mujeres en el estudio de las relaciones mujer-hombre y mujer-mujer, la segunda tenía una visión más holística ya que planteaba que hay que estudiar la sociedad ya que la subordinación de las mujeres es producto de la organización de esta, y que no se avanzará solamente estudiando a las mujeres, pues el estudio debe ser más amplio y en diferentes niveles, ámbitos y tiempos.
Es en esta búsqueda donde nace y se desarrolla el concepto de género como categoría social. Es así que los sistemas de género/sexo fueron entendidos como conjuntos de prácticas, símbolos, representaciones, normas y valores sociales que las sociedades construyen a partir de la diferencia anatomofisiológica y que dotan de sentido a los impulsos sexuales, la reproducción y en general a las relaciones de las personas. Por tanto, este sistema pasó a ser el objeto de estudio para comprender la subordinación de la mujer al hombre. Al ser el reconocimiento de una dimensión de la desigualdad social hasta entonces desconocida, se considera la ruptura epistemológica más importante de la segunda mitad del siglo pasado.
 Imagen representativa del binarismo de género
Imagen representativa del binarismo de géneroHay que decir que los fenómenos sociales se definen por la relación que guardan entre sí. Es así que la contextualización adquiere gran importancia. Varones y hembras tenemos la capacidad de producir con el cuerpo, pero solo los cuerpos de las hembras pueden gestar y por tanto asegurar la especie humana. Todo grupo humano que pretenda sobrevivir debe asegurarse cierto número de hembras que lo hagan posible. De ahí un poder particular del cuerpo de las hembras que además es económicamente útil. Dicho poder no es en tanto entidad biológica, sino que es la sociedad la que le otorga este poder. En este punto es importante preguntarnos históricamente ¿quiénes han controlado la capacidad reproductiva de las mujeres?, ¿quiénes han tenido la preferencia en el acceso sexual? Para asegurar un control efectivo sobre la reproducción es necesario asegurar el acceso a la sexualidad.
Ello también lleva a dirigir el trabajo que hacen porque de lo contrario, las mujeres pudieran tener espacio para representar una amenaza al dominio de los hombres. Es importante atender a las etapas del desarrollo de las mujeres, que permitirá ver cómo se moldean para aceptar la desigualdad y las jerarquías según el género en las distintas sociedades y culturas.
Otro contexto a delimitar es el ámbito doméstico donde históricamente ha estado ubicada la subordinación femenina. Se ha puesto al descubierto que en mujeres que comparten la misma posición de clase y raza, la condición femenina se redefine a lo largo de la vida y que algunas mujeres gozan de poder sobre otras aún en contextos de alta dominación masculina, donde se les inviste de autoridad, creando el sistema zonas de incertidumbre que las divide como género e impide alianzas y se legitima la dominación. Foucault decía que «el poder se ejerce, no se posee», siempre está en peligro de perderse y no basta con normas, leyes, amenazas o castigos. De ahí que los espacios de subordinación sean también espacios de poder de las mujeres. Es en estos espacios donde aparece la inseguridad, la tensión, la confrontación y por ejemplo, las mujeres pueden reclamar la anticoncepción.
Para terminar, es importante tener en cuenta que el género es una forma de desigualdad social que siempre está articulado con otras formas de desigualdad ya sea clase, raza, grupo etario, etc. Hay que pensar la dominación masculina con un comienzo vago en el tiempo, pero que permite desligar la subordinación de las mujeres de la evolución «natural» de la humanidad y entenderla como un proceso histórico. En ese sentido es necesario destacar que, respecto a la raza, en sociedades plurales hay que atender al contexto étnico-cultural ya que en dependencia de las relaciones entre personas de razas distintas, estarán condicionadas las relaciones entre los géneros.
 Imagen de mujeres de distintas razas
Imagen de mujeres de distintas razasPor otro lado, si bien es sabido que históricamente el sistema de género social imperante ha contribuido a invisibilizar a la mujer, asociar necesariamente dicha categoría únicamente a ella, lo que hace es nuevamente recrear el absolutismo histórico que tanto daño ha hecho, ahora como lo antagónico al hombre. En la construcción social participan todos los individuos presentes en el sistema género.
Hasta aquí la publicación de hoy, de la cual aun se puede ahondar mucho más, sobre todo en lo referido al origen de la dominación o de la jerarquización del binomio «hombre/mujer» desde un punto de vista antropológico, pero eso quedará pendiente para otro momento. ¡Así que hasta la próxima!, ¡nos vemos en Nostr!
........................................
English version
Hello nostriches. Today I want to make a post by way of an approach to the emergence of the categories of gender and feminism. So if you are interested in the topic make an effort, stay and read to the end.
The "new" feminism emerged in the 60's in those developed countries that agreed to recognize the human rights contained in the respective UN declaration. Then, as an extension of that recognition, the feminist movement was born. From then on, the relationship between nature and culture was raised again and the conclusion was reached that social differences go beyond biological differences, which has to do with the fact that even the satisfaction of elementary needs such as food, housing or clothing are conditioned by social constructions.
It turns out that one of the first proposals identified female subordination as a product of a patriarchal organization, taking Max Weber's category of patriarchy. This is how the vision of patriarchy was extended to political and academic discourse. However, there was no information about the historical development of this category, systematization, variations, etc., because it was something that was only recently perceived in society.
However, the same category of patriarchy, together with that of power relations to explain contemporary social phenomena, constitutes one of the main contributions of feminism. This is how they have first made visible and then deconstructed and dismantled a series of existing patterns in the culture that made women subordinate to men, and that were present in the sex/gender system.
 Image relating to the fight against patriarchy
Image relating to the fight against patriarchyUp to that time, in sociological research, an excessive androcentrism could be observed as scientific discourse revolved around men as the subject and object of research. Even for many positivists such as Weber himself, the problems related to women remained in the background and were blamed on a supposed passivity in the domestic-family sphere. This passivity was based on the supposed biological inferiority of the female gender.
Patriarchy was then an empty category in itself, with no explanatory value. From the political point of view, it could be useful for mobilization, but it did not resist the polemic of feminism's critics, nor did it problematize the conflicts to be resolved. But on the other hand, a group of women - mainly academics - set to work on a smaller task but with greater results in the long run. They set out to generate knowledge about women's living conditions, to search in the past and present for women's contributions to society, to make them visible in history. This is how academic centers, NGOs, projects, women's studies centers, etc., came into being.
It would be convenient to distinguish then two postures that accompanied the research on women: one that takes women as the object of study; living conditions, work, culture, and the other that privileges society as the generator of women's subordination. While the first perspective generated knowledge about women in the study of woman-man and woman-woman relations, the second had a more holistic vision, since it proposed that society must be studied, since the subordination of women is a product of its organization, and that progress will not be made only by studying women, since the study must be broader and at different levels, spheres and times.
It is in this search that the concept of gender as a social category was born and developed. Thus, gender/sex systems were understood as a set of practices, symbols, representations, norms and social values that societies construct on the basis of anatomophysiological differences and that give meaning to sexual impulses, reproduction and, in general, to people's relationships. Therefore, this system became the object of study to understand the subordination of women to men. As the recognition of a hitherto unknown dimension of social inequality, it is considered the most important epistemological breakthrough of the second half of the last century.
 Representative image of gender binarism
Representative image of gender binarismIt must be said that social phenomena are defined by their relationship with each other. Thus, contextualization acquires great importance. Males and females have the capacity to produce with their bodies, but only the bodies of females can gestate and therefore ensure the human species. Any human group that intends to survive must ensure a certain number of females to make it possible. Hence a particular power of the female body, which is also economically useful. This power is not as a biological entity, but it is society that gives it this power. At this point it is important to ask ourselves historically, who has controlled the reproductive capacity of women, who has had the preference in sexual access? To ensure effective control over reproduction, it is necessary to ensure access to sexuality.
 Allegorical image of pregnancy
Allegorical image of pregnancyThis also leads to directing the work they do because otherwise, women may have room to pose a threat to men's dominance. It is important to pay attention to the stages of women's development, which will allow us to see how they are shaped to accept inequality and gender hierarchies in different societies and cultures.
Another context to delimit is the domestic sphere where female subordination has historically been located. It has been discovered that in women who share the same class and race position, the feminine condition is redefined throughout life and that some women enjoy power over others even in contexts of high male domination, where they are invested with authority, creating the system of uncertainty zones that divide them as a gender and prevent alliances and legitimize domination. Foucault said that "power is exercised, not possessed", it is always in danger of being lost and norms, laws, threats or punishments are not enough. Hence, the spaces of subordination are also spaces of women's power. It is in these spaces where insecurity, tension, confrontation appear and where, for example, women can demand contraception.
To conclude, it is important to keep in mind that gender is a form of social inequality that is always articulated with other forms of inequality, be it class, race, age group, etc. It is necessary to think of male domination with a vague beginning in time, but which allows us to separate the subordination of women from the "natural" evolution of humanity and to understand it as a historical process. In this sense, it is necessary to emphasize that, with respect to race, in plural societies it is necessary to pay attention to the ethno-cultural context since, depending on the relations between people of different races, the relations between genders will be conditioned.
 Image of women of different races
Image of women of different racesOn the other hand, although it is known that historically the prevailing social gender system has contributed to make women invisible, to necessarily associate this category only to women is to recreate the historical absolutism that has done so much damage, this time as antagonistic to men. All individuals present in the gender system participate in the social construction.
So much for today's publication, of which we can still go much deeper, especially with regard to the origin of domination or the hierarchization of the binomial "man/woman" from an anthropological point of view, but that will be left for another time. So until next time, see you in Nostr!
Créditos | Credits
Bibliografía consultada | Consulted bibliography:
-
Barbieri, T. (1993). Sobre la categoría género. Una introducción teórico-metodológica. Debates en Sociología. (18). 1-19. https://doi.org/10.18800/debatesensociologia.199301.006
-
Echevarría, D. (2020). Desigualdades de género e interseccionalidad. Análisis del contexto cubano 2008-2018. Facultad Latinoamericana de Ciencias Sociales (Programa-Cuba). https://www.clacso.org.ar/libreria-latinoamericana-cm/libro_detalle_resultado.php?id_libro=2346&campo=cm&texto=248
Traducción | Translation:
DeepL
-
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ f33c8a96:5ec6f741
2024-04-16 21:15:01
@ f33c8a96:5ec6f741
2024-04-16 21:15:01 -
 @ db862490:e133503d
2024-04-15 22:20:07
@ db862490:e133503d
2024-04-15 22:20:07test test test
-
 @ fa0165a0:03397073
2023-10-06 19:25:08
@ fa0165a0:03397073
2023-10-06 19:25:08I just tested building a browser plugin, it was easier than I thought. Here I'll walk you through the steps of creating a minimal working example of a browser plugin, a.k.a. the "Hello World" of browser plugins.
First of all there are two main browser platforms out there, Chromium and Mozilla. They do some things a little differently, but similar enough that we can build a plugin that works on both. This plugin will work in both, I'll describe the firefox version, but the chromium version is very similar.
What is a browser plugin?
Simply put, a browser plugin is a program that runs in the browser. It can do things like modify the content of a webpage, or add new functionality to the browser. It's a way to extend the browser with custom functionality. Common examples are ad blockers, password managers, and video downloaders.
In technical terms, they are plugins that can insert html-css-js into your browser experience.
How to build a browser plugin
Step 0: Basics
You'll need a computer, a text editor and a browser. For testing and development I personally think that the firefox developer edition is the easiest to work with. But any Chrome based browser will also do.
Create a working directory on your computer, name it anything you like. I'll call mine
hello-world-browser-plugin. Open the directory and create a file calledmanifest.json. This is the most important file of your plugin, and it must be named exactly right.Step 1: manifest.json
After creation open your file
manifest.jsonin your text editor and paste the following code:json { "manifest_version": 3, "name": "Hello World", "version": "1.0", "description": "A simple 'Hello World' browser extension", "content_scripts": [ { "matches": ["<all_urls>"], "js": ["hello.js"] //The name of your script file. // "css": ["hello.css"] //The name of your css file. } ] }If you wonder what the
jsonfile format is, it's a normal text file with a special syntax such that a computer can easily read it. It's thejsonsyntax you see in the code above. Let's go through what's being said here. (If you are not interested, just skip to the next step after pasting this we are done here.)manifest_version: This is the version of the manifest file format. It's currently at version 3, and it's the latest version. It's important that you set this to 3, otherwise your plugin won't work.name: This is the name of your plugin. It can be anything you like.version: This is the version of your plugin. It can be anything you like.description: This is the description of your plugin. It can be anything you like.content_scripts: This is where you define what your plugin does. It's a list of scripts that will be executed when the browser loads a webpage. In this case we have one script, calledhello.js. It's the script that we'll create in the next step.matches: This is a list of urls that the script will be executed on. In this case we have<all_urls>, which means that the script will be executed on all urls. You can also specify a specific url, likehttps://brave.com/*, which means that the script will only be executed on urls that start withhttps://brave.com/.js: This is a list of javascript files that will be executed. In this case we have one file, calledhello.js. It's the script that we'll create in the next step.css: This is where you can add a list of css files that will be executed. In this case we have none, but you can add css files here if you want to.//: Text following these two characters are comments. They are ignored by the computer, You can add comments anywhere you like, and they are a good way to document your code.
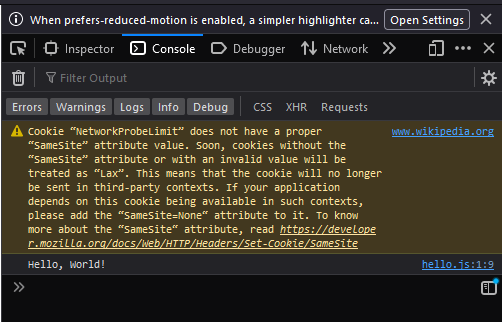
Step 2: hello.js
Now it's time to create another file in your project folder. This time we'll call it
hello.js. When created, open it in your text editor and paste the following code:js console.log("Hello World!");That's javascript code, and it's what will be executed when you run your plugin. It's a simpleconsole.logstatement, which will print the text "Hello World!" to the console. The console is a place where the browser prints out messages, and it's a good place to start when debugging your plugin.Step 3: Load and launch your plugin
Firefox
Now it's time to load your plugin into your browser. Open your browser and go to the url
about:debugging#/runtime/this-firefox. You should see a page that looks something like this: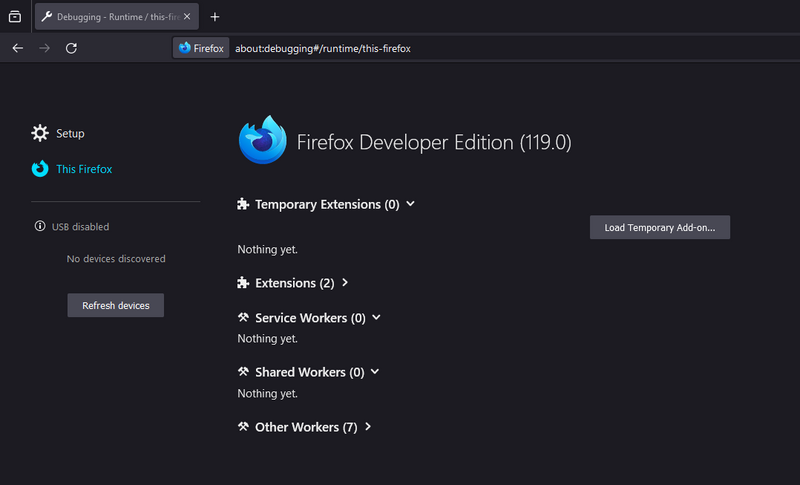
Click the button that says "Load Temporary Add-on...". A file dialog will open, navigate to your project folder and select the file
manifest.json. Your plugin should now be loaded and running.Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
Chrome
Open your browser and go to the url
chrome://extensions/. Click the button that says "Load unpacked". A file dialog will open, navigate to your project folder and select the folderhello-world-browser-plugin. Your plugin should now be loaded and running.Note the difference, of selecting the file
manifest.jsonin firefox, and selecting the folderhello-world-browser-pluginin chrome. Otherwise, the process is the same. So I'll repeat the same text as above: (for those who skipped ahead..)Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
As you can see this isn't as complicated as one might think. Having preformed a "Hello-World!"-project is a very useful and valuable first step. These setup steps are the basics for any browser plugin, and you can build on this to create more advanced plugins.
-
 @ c7eda660:efd97c86
2024-04-14 02:02:19
@ c7eda660:efd97c86
2024-04-14 02:02:19This is a test of Nostr Writer, publishing from Obsidian.
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ bcea2b98:7ccef3c9
2024-04-11 02:25:20
@ bcea2b98:7ccef3c9
2024-04-11 02:25:20 -
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note
-
 @ 000002de:c05780a7
2024-04-05 18:58:16
@ 000002de:c05780a7
2024-04-05 18:58:16I don't have much concern for the US attempting an outright ban any more. That ship has sailed unless the US gets very disparate. The issue that most concerns me is that there is a slow move away from self custody by bitcoiners.
-
 @ 8fb140b4:f948000c
2023-07-22 09:39:48
@ 8fb140b4:f948000c
2023-07-22 09:39:48Intro
This short tutorial will help you set up your own Nostr Wallet Connect (NWC) on your own LND Node that is not using Umbrel. If you are a user of Umbrel, you should use their version of NWC.
Requirements
You need to have a working installation of LND with established channels and connectivity to the internet. NWC in itself is fairly light and will not consume a lot of resources. You will also want to ensure that you have a working installation of Docker, since we will use a docker image to run NWC.
- Working installation of LND (and all of its required components)
- Docker (with Docker compose)
Installation
For the purpose of this tutorial, we will assume that you have your lnd/bitcoind running under user bitcoin with home directory /home/bitcoin. We will also assume that you already have a running installation of Docker (or docker.io).
Prepare and verify
git version - we will need git to get the latest version of NWC. docker version - should execute successfully and show the currently installed version of Docker. docker compose version - same as before, but the version will be different. ss -tupln | grep 10009- should produce the following output: tcp LISTEN 0 4096 0.0.0.0:10009 0.0.0.0: tcp LISTEN 0 4096 [::]:10009 [::]:**
For things to work correctly, your Docker should be version 20.10.0 or later. If you have an older version, consider installing a new one using instructions here: https://docs.docker.com/engine/install/
Create folders & download NWC
In the home directory of your LND/bitcoind user, create a new folder, e.g., "nwc" mkdir /home/bitcoin/nwc. Change to that directory cd /home/bitcoin/nwc and clone the NWC repository: git clone https://github.com/getAlby/nostr-wallet-connect.git
Creating the Docker image
In this step, we will create a Docker image that you will use to run NWC.
- Change directory to
nostr-wallet-connect:cd nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - The last line of the output (after a few minutes) should look like
=> => naming to docker.io/library/nwc:latest nwc:latestis the name of the Docker image with a tag which you should note for use later.
Creating docker-compose.yml and necessary data directories
- Let's create a directory that will hold your non-volatile data (DB):
mkdir data - In
docker-compose.ymlfile, there are fields that you want to replace (<> comments) and port “4321” that you want to make sure is open (check withss -tupln | grep 4321which should return nothing). - Create
docker-compose.ymlfile with the following content, and make sure to update fields that have <> comment:
version: "3.8" services: nwc: image: nwc:latest volumes: - ./data:/data - ~/.lnd:/lnd:ro ports: - "4321:8080" extra_hosts: - "localhost:host-gateway" environment: NOSTR_PRIVKEY: <use "openssl rand -hex 32" to generate a fresh key and place it inside ""> LN_BACKEND_TYPE: "LND" LND_ADDRESS: localhost:10009 LND_CERT_FILE: "/lnd/tls.cert" LND_MACAROON_FILE: "/lnd/data/chain/bitcoin/mainnet/admin.macaroon" DATABASE_URI: "/data/nostr-wallet-connect.db" COOKIE_SECRET: <use "openssl rand -hex 32" to generate fresh secret and place it inside ""> PORT: 8080 restart: always stop_grace_period: 1mStarting and testing
Now that you have everything ready, it is time to start the container and test.
- While you are in the
nwcdirectory (important), execute the following command and check the log output,docker compose up - You should see container logs while it is starting, and it should not exit if everything went well.
- At this point, you should be able to go to
http://<ip of the host where nwc is running>:4321and get to the interface of NWC - To stop the test run of NWC, simply press
Ctrl-C, and it will shut the container down. - To start NWC permanently, you should execute
docker compose up -d, “-d” tells Docker to detach from the session. - To check currently running NWC logs, execute
docker compose logsto run it in tail mode add-fto the end. - To stop the container, execute
docker compose down
That's all, just follow the instructions in the web interface to get started.
Updating
As with any software, you should expect fixes and updates that you would need to perform periodically. You could automate this, but it falls outside of the scope of this tutorial. Since we already have all of the necessary configuration in place, the update execution is fairly simple.
- Change directory to the clone of the git repository,
cd /home/bitcoin/nwc/nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - Change directory back one level
cd .. - Restart (stop and start) the docker compose config
docker compose down && docker compose up -d - Done! Optionally you may want to check the logs:
docker compose logs
-
 @ c384de42:493922aa
2024-04-05 01:03:01
@ c384de42:493922aa
2024-04-05 01:03:01Sometimes I wonder if any and all sorting algorithms have a conscious experience and how many possible variations of sorting algorithms could possibly exist.
-
 @ d2e97f73:ea9a4d1b
2023-04-11 19:36:53
@ d2e97f73:ea9a4d1b
2023-04-11 19:36:53There’s a lot of conversation around the #TwitterFiles. Here’s my take, and thoughts on how to fix the issues identified.
I’ll start with the principles I’ve come to believe…based on everything I’ve learned and experienced through my past actions as a Twitter co-founder and lead:
- Social media must be resilient to corporate and government control.
- Only the original author may remove content they produce.
- Moderation is best implemented by algorithmic choice.
The Twitter when I led it and the Twitter of today do not meet any of these principles. This is my fault alone, as I completely gave up pushing for them when an activist entered our stock in 2020. I no longer had hope of achieving any of it as a public company with no defense mechanisms (lack of dual-class shares being a key one). I planned my exit at that moment knowing I was no longer right for the company.
The biggest mistake I made was continuing to invest in building tools for us to manage the public conversation, versus building tools for the people using Twitter to easily manage it for themselves. This burdened the company with too much power, and opened us to significant outside pressure (such as advertising budgets). I generally think companies have become far too powerful, and that became completely clear to me with our suspension of Trump’s account. As I’ve said before, we did the right thing for the public company business at the time, but the wrong thing for the internet and society. Much more about this here: https://twitter.com/jack/status/1349510769268850690
I continue to believe there was no ill intent or hidden agendas, and everyone acted according to the best information we had at the time. Of course mistakes were made. But if we had focused more on tools for the people using the service rather than tools for us, and moved much faster towards absolute transparency, we probably wouldn’t be in this situation of needing a fresh reset (which I am supportive of). Again, I own all of this and our actions, and all I can do is work to make it right.
Back to the principles. Of course governments want to shape and control the public conversation, and will use every method at their disposal to do so, including the media. And the power a corporation wields to do the same is only growing. It’s critical that the people have tools to resist this, and that those tools are ultimately owned by the people. Allowing a government or a few corporations to own the public conversation is a path towards centralized control.
I’m a strong believer that any content produced by someone for the internet should be permanent until the original author chooses to delete it. It should be always available and addressable. Content takedowns and suspensions should not be possible. Doing so complicates important context, learning, and enforcement of illegal activity. There are significant issues with this stance of course, but starting with this principle will allow for far better solutions than we have today. The internet is trending towards a world were storage is “free” and infinite, which places all the actual value on how to discover and see content.
Which brings me to the last principle: moderation. I don’t believe a centralized system can do content moderation globally. It can only be done through ranking and relevance algorithms, the more localized the better. But instead of a company or government building and controlling these solely, people should be able to build and choose from algorithms that best match their criteria, or not have to use any at all. A “follow” action should always deliver every bit of content from the corresponding account, and the algorithms should be able to comb through everything else through a relevance lens that an individual determines. There’s a default “G-rated” algorithm, and then there’s everything else one can imagine.
The only way I know of to truly live up to these 3 principles is a free and open protocol for social media, that is not owned by a single company or group of companies, and is resilient to corporate and government influence. The problem today is that we have companies who own both the protocol and discovery of content. Which ultimately puts one person in charge of what’s available and seen, or not. This is by definition a single point of failure, no matter how great the person, and over time will fracture the public conversation, and may lead to more control by governments and corporations around the world.
I believe many companies can build a phenomenal business off an open protocol. For proof, look at both the web and email. The biggest problem with these models however is that the discovery mechanisms are far too proprietary and fixed instead of open or extendable. Companies can build many profitable services that complement rather than lock down how we access this massive collection of conversation. There is no need to own or host it themselves.
Many of you won’t trust this solution just because it’s me stating it. I get it, but that’s exactly the point. Trusting any one individual with this comes with compromises, not to mention being way too heavy a burden for the individual. It has to be something akin to what bitcoin has shown to be possible. If you want proof of this, get out of the US and European bubble of the bitcoin price fluctuations and learn how real people are using it for censorship resistance in Africa and Central/South America.
I do still wish for Twitter, and every company, to become uncomfortably transparent in all their actions, and I wish I forced more of that years ago. I do believe absolute transparency builds trust. As for the files, I wish they were released Wikileaks-style, with many more eyes and interpretations to consider. And along with that, commitments of transparency for present and future actions. I’m hopeful all of this will happen. There’s nothing to hide…only a lot to learn from. The current attacks on my former colleagues could be dangerous and doesn’t solve anything. If you want to blame, direct it at me and my actions, or lack thereof.
As far as the free and open social media protocol goes, there are many competing projects: @bluesky is one with the AT Protocol, nostr another, Mastodon yet another, Matrix yet another…and there will be many more. One will have a chance at becoming a standard like HTTP or SMTP. This isn’t about a “decentralized Twitter.” This is a focused and urgent push for a foundational core technology standard to make social media a native part of the internet. I believe this is critical both to Twitter’s future, and the public conversation’s ability to truly serve the people, which helps hold governments and corporations accountable. And hopefully makes it all a lot more fun and informative again.
💸🛠️🌐 To accelerate open internet and protocol work, I’m going to open a new category of #startsmall grants: “open internet development.” It will start with a focus of giving cash and equity grants to engineering teams working on social media and private communication protocols, bitcoin, and a web-only mobile OS. I’ll make some grants next week, starting with $1mm/yr to Signal. Please let me know other great candidates for this money.
-
 @ ae1008d2:a166d760
2024-04-04 17:21:52
@ ae1008d2:a166d760
2024-04-04 17:21:52I'm testing this to make sure I can post here on highlighter
-
 @ 82341f88:fbfbe6a2
2023-04-11 19:36:53
@ 82341f88:fbfbe6a2
2023-04-11 19:36:53There’s a lot of conversation around the #TwitterFiles. Here’s my take, and thoughts on how to fix the issues identified.
I’ll start with the principles I’ve come to believe…based on everything I’ve learned and experienced through my past actions as a Twitter co-founder and lead:
- Social media must be resilient to corporate and government control.
- Only the original author may remove content they produce.
- Moderation is best implemented by algorithmic choice.
The Twitter when I led it and the Twitter of today do not meet any of these principles. This is my fault alone, as I completely gave up pushing for them when an activist entered our stock in 2020. I no longer had hope of achieving any of it as a public company with no defense mechanisms (lack of dual-class shares being a key one). I planned my exit at that moment knowing I was no longer right for the company.
The biggest mistake I made was continuing to invest in building tools for us to manage the public conversation, versus building tools for the people using Twitter to easily manage it for themselves. This burdened the company with too much power, and opened us to significant outside pressure (such as advertising budgets). I generally think companies have become far too powerful, and that became completely clear to me with our suspension of Trump’s account. As I’ve said before, we did the right thing for the public company business at the time, but the wrong thing for the internet and society. Much more about this here: https://twitter.com/jack/status/1349510769268850690
I continue to believe there was no ill intent or hidden agendas, and everyone acted according to the best information we had at the time. Of course mistakes were made. But if we had focused more on tools for the people using the service rather than tools for us, and moved much faster towards absolute transparency, we probably wouldn’t be in this situation of needing a fresh reset (which I am supportive of). Again, I own all of this and our actions, and all I can do is work to make it right.
Back to the principles. Of course governments want to shape and control the public conversation, and will use every method at their disposal to do so, including the media. And the power a corporation wields to do the same is only growing. It’s critical that the people have tools to resist this, and that those tools are ultimately owned by the people. Allowing a government or a few corporations to own the public conversation is a path towards centralized control.
I’m a strong believer that any content produced by someone for the internet should be permanent until the original author chooses to delete it. It should be always available and addressable. Content takedowns and suspensions should not be possible. Doing so complicates important context, learning, and enforcement of illegal activity. There are significant issues with this stance of course, but starting with this principle will allow for far better solutions than we have today. The internet is trending towards a world were storage is “free” and infinite, which places all the actual value on how to discover and see content.
Which brings me to the last principle: moderation. I don’t believe a centralized system can do content moderation globally. It can only be done through ranking and relevance algorithms, the more localized the better. But instead of a company or government building and controlling these solely, people should be able to build and choose from algorithms that best match their criteria, or not have to use any at all. A “follow” action should always deliver every bit of content from the corresponding account, and the algorithms should be able to comb through everything else through a relevance lens that an individual determines. There’s a default “G-rated” algorithm, and then there’s everything else one can imagine.
The only way I know of to truly live up to these 3 principles is a free and open protocol for social media, that is not owned by a single company or group of companies, and is resilient to corporate and government influence. The problem today is that we have companies who own both the protocol and discovery of content. Which ultimately puts one person in charge of what’s available and seen, or not. This is by definition a single point of failure, no matter how great the person, and over time will fracture the public conversation, and may lead to more control by governments and corporations around the world.
I believe many companies can build a phenomenal business off an open protocol. For proof, look at both the web and email. The biggest problem with these models however is that the discovery mechanisms are far too proprietary and fixed instead of open or extendable. Companies can build many profitable services that complement rather than lock down how we access this massive collection of conversation. There is no need to own or host it themselves.
Many of you won’t trust this solution just because it’s me stating it. I get it, but that’s exactly the point. Trusting any one individual with this comes with compromises, not to mention being way too heavy a burden for the individual. It has to be something akin to what bitcoin has shown to be possible. If you want proof of this, get out of the US and European bubble of the bitcoin price fluctuations and learn how real people are using it for censorship resistance in Africa and Central/South America.
I do still wish for Twitter, and every company, to become uncomfortably transparent in all their actions, and I wish I forced more of that years ago. I do believe absolute transparency builds trust. As for the files, I wish they were released Wikileaks-style, with many more eyes and interpretations to consider. And along with that, commitments of transparency for present and future actions. I’m hopeful all of this will happen. There’s nothing to hide…only a lot to learn from. The current attacks on my former colleagues could be dangerous and doesn’t solve anything. If you want to blame, direct it at me and my actions, or lack thereof.
As far as the free and open social media protocol goes, there are many competing projects: @bluesky is one with the AT Protocol, nostr another, Mastodon yet another, Matrix yet another…and there will be many more. One will have a chance at becoming a standard like HTTP or SMTP. This isn’t about a “decentralized Twitter.” This is a focused and urgent push for a foundational core technology standard to make social media a native part of the internet. I believe this is critical both to Twitter’s future, and the public conversation’s ability to truly serve the people, which helps hold governments and corporations accountable. And hopefully makes it all a lot more fun and informative again.
💸🛠️🌐 To accelerate open internet and protocol work, I’m going to open a new category of #startsmall grants: “open internet development.” It will start with a focus of giving cash and equity grants to engineering teams working on social media and private communication protocols, bitcoin, and a web-only mobile OS. I’ll make some grants next week, starting with $1mm/yr to Signal. Please let me know other great candidates for this money.
-
 @ facf399f:70977863
2024-04-02 14:12:09
@ facf399f:70977863
2024-04-02 14:12:09I'm on Obsidian, but I'm also on NOSTR. Test 123.
-
 @ bcea2b98:7ccef3c9
2024-04-01 17:27:32
@ bcea2b98:7ccef3c9
2024-04-01 17:27:32I've used Librovox, but looking for more recent technical and fiction topics. Audible seems so expensive having to pay for books in addition to a monthly membership. It would be nice if I could "browse" and listen to a lot of different types of books.
-
 @ 5d4b6c8d:8a1c1ee3
2024-03-29 22:37:11
@ 5d4b6c8d:8a1c1ee3
2024-03-29 22:37:11https://youtu.be/zf8LkBWEEQ8?si=JuKtzUKHBdEzsVTZ
-
 @ f33c8a96:5ec6f741
2024-03-27 18:07:49
@ f33c8a96:5ec6f741
2024-03-27 18:07:49The standard Lorem Ipsum passage, used since the 1500s
"Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum."
Section 1.10.32 of "de Finibus Bonorum et Malorum", written by Cicero in 45 BC
"Sed ut perspiciatis unde omnis iste natus error sit voluptatem accusantium doloremque laudantium, totam rem aperiam, eaque ipsa quae ab illo inventore veritatis et quasi architecto beatae vitae dicta sunt explicabo. Nemo enim ipsam voluptatem quia voluptas sit aspernatur aut odit aut fugit, sed quia consequuntur magni dolores eos qui ratione voluptatem sequi nesciunt. Neque porro quisquam est, qui dolorem ipsum quia dolor sit amet, consectetur, adipisci velit, sed quia non numquam eius modi tempora incidunt ut labore et dolore magnam aliquam quaerat voluptatem. Ut enim ad minima veniam, quis nostrum exercitationem ullam corporis suscipit laboriosam, nisi ut aliquid ex ea commodi consequatur? Quis autem vel eum iure reprehenderit qui in ea voluptate velit esse quam nihil molestiae consequatur, vel illum qui dolorem eum fugiat quo voluptas nulla pariatur?"
1914 translation by H. Rackham
"But I must explain to you how all this mistaken idea of denouncing pleasure and praising pain was born and I will give you a complete account of the system, and expound the actual teachings of the great explorer of the truth, the master-builder of human happiness. No one rejects, dislikes, or avoids pleasure itself, because it is pleasure, but because those who do not know how to pursue pleasure rationally encounter consequences that are extremely painful. Nor again is there anyone who loves or pursues or desires to obtain pain of itself, because it is pain, but because occasionally circumstances occur in which toil and pain can procure him some great pleasure. To take a trivial example, which of us ever undertakes laborious physical exercise, except to obtain some advantage from it? But who has any right to find fault with a man who chooses to enjoy a pleasure that has no annoying consequences, or one who avoids a pain that produces no resultant pleasure?"
Section 1.10.33 of "de Finibus Bonorum et Malorum", written by Cicero in 45 BC
"At vero eos et accusamus et iusto odio dignissimos ducimus qui blanditiis praesentium voluptatum deleniti atque corrupti quos dolores et quas molestias excepturi sint occaecati cupiditate non provident, similique sunt in culpa qui officia deserunt mollitia animi, id est laborum et dolorum fuga. Et harum quidem rerum facilis est et expedita distinctio. Nam libero tempore, cum soluta nobis est eligendi optio cumque nihil impedit quo minus id quod maxime placeat facere possimus, omnis voluptas assumenda est, omnis dolor repellendus. Temporibus autem quibusdam et aut officiis debitis aut rerum necessitatibus saepe eveniet ut et voluptates repudiandae sint et molestiae non recusandae. Itaque earum rerum hic tenetur a sapiente delectus, ut aut reiciendis voluptatibus maiores alias consequatur aut perferendis doloribus asperiores repellat."
1914 translation by H. Rackham
"On the other hand, we denounce with righteous indignation and dislike men who are so beguiled and demoralized by the charms of pleasure of the moment, so blinded by desire, that they cannot foresee the pain and trouble that are bound to ensue; and equal blame belongs to those who fail in their duty through weakness of will, which is the same as saying through shrinking from toil and pain. These cases are perfectly simple and easy to distinguish. In a free hour, when our power of choice is untrammelled and when nothing prevents our being able to do what we like best, every pleasure is to be welcomed and every pain avoided. But in certain circumstances and owing to the claims of duty or the obligations of business it will frequently occur that pleasures have to be repudiated and annoyances accepted. The wise man therefore always holds in these matters to this principle of selection: he rejects pleasures to secure other greater pleasures, or else he endures pains to avoid worse pains."
-
 @ f33c8a96:5ec6f741
2024-03-27 18:02:25
@ f33c8a96:5ec6f741
2024-03-27 18:02:25The standard Lorem Ipsum passage, used since the 1500s
"Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum."
Section 1.10.32 of "de Finibus Bonorum et Malorum", written by Cicero in 45 BC
"Sed ut perspiciatis unde omnis iste natus error sit voluptatem accusantium doloremque laudantium, totam rem aperiam, eaque ipsa quae ab illo inventore veritatis et quasi architecto beatae vitae dicta sunt explicabo. Nemo enim ipsam voluptatem quia voluptas sit aspernatur aut odit aut fugit, sed quia consequuntur magni dolores eos qui ratione voluptatem sequi nesciunt. Neque porro quisquam est, qui dolorem ipsum quia dolor sit amet, consectetur, adipisci velit, sed quia non numquam eius modi tempora incidunt ut labore et dolore magnam aliquam quaerat voluptatem. Ut enim ad minima veniam, quis nostrum exercitationem ullam corporis suscipit laboriosam, nisi ut aliquid ex ea commodi consequatur? Quis autem vel eum iure reprehenderit qui in ea voluptate velit esse quam nihil molestiae consequatur, vel illum qui dolorem eum fugiat quo voluptas nulla pariatur?"
1914 translation by H. Rackham
"But I must explain to you how all this mistaken idea of denouncing pleasure and praising pain was born and I will give you a complete account of the system, and expound the actual teachings of the great explorer of the truth, the master-builder of human happiness. No one rejects, dislikes, or avoids pleasure itself, because it is pleasure, but because those who do not know how to pursue pleasure rationally encounter consequences that are extremely painful. Nor again is there anyone who loves or pursues or desires to obtain pain of itself, because it is pain, but because occasionally circumstances occur in which toil and pain can procure him some great pleasure. To take a trivial example, which of us ever undertakes laborious physical exercise, except to obtain some advantage from it? But who has any right to find fault with a man who chooses to enjoy a pleasure that has no annoying consequences, or one who avoids a pain that produces no resultant pleasure?"
Section 1.10.33 of "de Finibus Bonorum et Malorum", written by Cicero in 45 BC
"At vero eos et accusamus et iusto odio dignissimos ducimus qui blanditiis praesentium voluptatum deleniti atque corrupti quos dolores et quas molestias excepturi sint occaecati cupiditate non provident, similique sunt in culpa qui officia deserunt mollitia animi, id est laborum et dolorum fuga. Et harum quidem rerum facilis est et expedita distinctio. Nam libero tempore, cum soluta nobis est eligendi optio cumque nihil impedit quo minus id quod maxime placeat facere possimus, omnis voluptas assumenda est, omnis dolor repellendus. Temporibus autem quibusdam et aut officiis debitis aut rerum necessitatibus saepe eveniet ut et voluptates repudiandae sint et molestiae non recusandae. Itaque earum rerum hic tenetur a sapiente delectus, ut aut reiciendis voluptatibus maiores alias consequatur aut perferendis doloribus asperiores repellat."
1914 translation by H. Rackham
"On the other hand, we denounce with righteous indignation and dislike men who are so beguiled and demoralized by the charms of pleasure of the moment, so blinded by desire, that they cannot foresee the pain and trouble that are bound to ensue; and equal blame belongs to those who fail in their duty through weakness of will, which is the same as saying through shrinking from toil and pain. These cases are perfectly simple and easy to distinguish. In a free hour, when our power of choice is untrammelled and when nothing prevents our being able to do what we like best, every pleasure is to be welcomed and every pain avoided. But in certain circumstances and owing to the claims of duty or the obligations of business it will frequently occur that pleasures have to be repudiated and annoyances accepted. The wise man therefore always holds in these matters to this principle of selection: he rejects pleasures to secure other greater pleasures, or else he endures pains to avoid worse pains."
-
 @ 676c0224:e641b6d6
2024-03-25 18:37:25
@ 676c0224:e641b6d6
2024-03-25 18:37:25```
const buildEvent = (draft) => {
let event = {}; // Initialize the event object
let type; // Initialize the type variable
switch (draft?.type) {
case 'resource':
event = {
kind: draft?.price ? 30402 : 30023, // Determine kind based on if price is present
content: draft.content,
created_at: Math.floor(Date.now() / 1000),
tags: [
['d', draft.id],
['title', draft.title],
['summary', draft.summary],
['image', draft.image],
['t', ...draft.topics],
['published_at', Math.floor(Date.now() / 1000).toString()],
// Include price and location tags only if price is present
...(draft?.price ? [['price', draft.price], ['location', `https://plebdevs.com/resource/${draft.id}`]] : []),
]
};
type = 'resource';
break;
case 'workshop':
// Assuming workshop events have a similar structure to resources
// You can adjust the event structure and kind as necessary
event = {
kind: 30023, // Example kind for workshops
content: draft.content,
created_at: Math.floor(Date.now() / 1000),
tags: [
['d', draft.id],
['title', draft.title],
['summary', draft.summary],
['image', draft.image],
['t', ...draft.topics],
['published_at', Math.floor(Date.now() / 1000).toString()],
]
};
type = 'workshop';
break;
case 'course':
// Assuming course events have a similar structure
// Adjust as necessary for your application's logic
event = {
kind: 30023, // Example kind for courses
content: draft.content,
created_at: Math.floor(Date.now() / 1000),
tags: [
['d', draft.id],
['title', draft.title],
['summary', draft.summary],
['image', draft.image],
['t', ...draft.topics],
['published_at', Math.floor(Date.now() / 1000).toString()],
]
};
type = 'course';
break;
default:
// Handle unknown draft type or return a default structure if necessary
event = null;
type = 'unknown';
}
return { unsignedEvent: event, type }; // Return both the event and its type
};
```
-
 @ ec965405:63996966
2024-03-25 18:32:54
@ ec965405:63996966
2024-03-25 18:32:54Me gusta cocinar y bailar!
-
 @ 676c0224:e641b6d6
2024-03-25 15:03:52
@ 676c0224:e641b6d6
2024-03-25 15:03:52 -
 @ 5e73c80b:08433652
2024-03-24 22:48:31
@ 5e73c80b:08433652
2024-03-24 22:48:31I was just curious to hear your thoughts on this. I saw this on the Netflix show "Encounters" and it blew my mind.
-
 @ 676c0224:e641b6d6
2024-03-24 20:07:55
@ 676c0224:e641b6d6
2024-03-24 20:07:55test
-
 @ 676c0224:e641b6d6
2024-03-24 19:15:53
@ 676c0224:e641b6d6
2024-03-24 19:15:53haha I'm testing haha
-
 @ 676c0224:e641b6d6
2024-03-24 19:15:03
@ 676c0224:e641b6d6
2024-03-24 19:15:03haha I'm testing haha
-
 @ 676c0224:e641b6d6
2024-03-24 19:11:21
@ 676c0224:e641b6d6
2024-03-24 19:11:21testing hahatest
-
 @ 5e73c80b:08433652
2024-03-24 16:24:22
@ 5e73c80b:08433652
2024-03-24 16:24:22I'm sure you have all thought of this before but I haven't. If Bitcoin is so great what's to stop a different Satoshi Angel from immaculate conception of a similar idea. Let's call it Bytecoin. Let's say Bytecoin drops next year and in 10 years is ifinirly more popular and more utilized than Bitcoin. Your Bitcoin still has value but but will h less demand for Bitcoin and more for Bytecoin it not worth as much anymore. Would it really be that difficult to copy the Bitcoin idea? It seems like real success would be whatever coin is adopted more widely. Thoughts?
-
 @ 672d3933:eb0014ed
2024-03-23 19:15:44
@ 672d3933:eb0014ed
2024-03-23 19:15:44I've been aiming to put together some use-cases for small and medium size local and ecommerce businesses to start using and building with nostr and lightning. For context, I'm thinking local businesses that also have a web presence. I can see such cases applying to both internal (private) and external (customer facing). There are obvious use-cases, like social media and lightning payments at a store-front. However, I'd like to expand thinking into everyday operations - any thoughts?
-
 @ 83defd06:45cb69da
2024-03-21 00:38:55
@ 83defd06:45cb69da
2024-03-21 00:38:55EfBdNCE5zHbPze41Jz3IwQ==?iv=ZZYHPnIFe4c5F5oWTmmpsw==
-
 @ c3a7907e:e2e696d2
2024-03-19 15:11:35
@ c3a7907e:e2e696d2
2024-03-19 15:11:35Hi all, this is John and the Zaprite team. Feel free to ask us anything. Zaprite is a non-custodial payments platform offering merchant tools for getting paid in bitcoin. You can learn more at zaprite.com
-
 @ 20d29810:6fe4ad2f
2024-03-15 20:51:56
@ 20d29810:6fe4ad2f
2024-03-15 20:51:56













































-
 @ 000002de:c05780a7
2024-03-13 03:23:14
@ 000002de:c05780a7
2024-03-13 03:23:14I've been going through Base58's bitcoin dev course and I am enjoying it quite a bit. For me, I think its the combination of the various technologies. The deeper I get into it the more respect I have for Satoshi and the developers that have built bitcoin. It may be old news to those of you that work on bitcoin projects every day but I'm pretty excited about how it all works still.
-
 @ f04fd50c:c371fda8
2024-03-12 23:26:48
@ f04fd50c:c371fda8
2024-03-12 23:26:48How far does this go out now?
-
 @ f3b691eb:aa9a5c31
2024-03-12 12:26:20
@ f3b691eb:aa9a5c31
2024-03-12 12:26:20 -
 @ c6bef3ed:890586d5
2024-03-10 17:26:31
@ c6bef3ed:890586d5
2024-03-10 17:26:31 -
 @ c6bef3ed:890586d5
2024-03-10 17:19:58
@ c6bef3ed:890586d5
2024-03-10 17:19:58 -
 @ 502ab02a:a2860397
2024-04-24 09:27:28
@ 502ab02a:a2860397
2024-04-24 09:27:28หลายๆครั้งที่เรากินเฮฟวีครีมหรือที่บ้านเราเรียกวิปครีม ไม่หมดแถมใกล้จะหมดอายุแล้วด้วย เราสามารถนำมาเรียนรู้กระบวนการผลิตสิ่งที่เรียกว่า ผลิตภัณฑ์จากนม หรือ Dairy Product ได้ครับ แถมเรายังได้ของไว้ใช้ทำอาหารอีกด้วย นั่นคือ การทำครีมให้เป็นเนย แล้วเอาเนยไปทำกี อีกที งว่ออออออ
ผมจะเล่าสิ่งที่ผมทำเล่นๆเป็นงานอดิเรกให้อ่านกันครับ
ส่วนตัวแล้วผมค่อนข้างหลงไหลใน ไขมันเนย และสนุกในการเรียนรู้มันมานานพอสมควร รวมถึงได้คลุกคลีกับอุตสาหกรรมนม มาตั้งแต่ราวๆปี 2001 ที่น่าสนใจคือ สัดส่วนสารอาหารของไขมันเนย ดีงามตั้งแต่เรื่อง กรดไขมันสายสั้น สัดส่วนที่ลงตัวระหว่างโอเมก้า3:6 รวมถึงมีกลิ่นหอมละมุน
กระบวนการทำเนยนั้น เขาก็จะนำนมมาแยกส่วนที่เป็นครีมออกมา เพื่อปั่นแยกไขมันเนยกับเวย์ ในขั้นตอนการแยกครีมนั้น เราจะได้ **ครีม(นมกับไขมันเนย) และ นมพร่องมันเนย (นมที่มีไขมันเนยต่ำ แน่สิมันไปอยู่ในครีมไง) **
ซึ่งนมพร่องมันเนยนี่ละครับ เป็นกระบวนการเดียวกับที่เขานำไปขายเป็นนมไขมันต่ำ หรือ ไม่ก็เอาไปทำนมผง(สกิมมิลค์) . . . แต่ทำความเข้าใจก่อนนะครับว่า บางโรงงานก็ไม่ได้เอาเศษพวกนี้มาทำของขายเรานะ โรงงานนมผงบางที่ก็เป้นการตั้งไลน์ทำขึ้นมาโดยเฉพาะแล้วได้ by product เป็นครีมแทน
คือมันไม่เหมือนกันระหว่าง ตั้งใจทำครีมออกมาขายแล้วได้หางนมมาทำนมผงนมไขมันต่ำ VS ตั้งใจทำนมผงนมไขมันต่ำมาขายแล้วได้เศษเหลือเป็นครีม
มันเป็นแค่กระบวนการที่คล้ายกันคือ มีการแยกครีมกับนม แต่การตั้งเครื่องไม่เหมือนกัน เขาจะตั้งเอาสิ่งที่ต้องการผลิตเป็นหลัก ที่เหลือมันจึงเป็นแค่ by product
โอเคทีนี้กลับมาเรื่องของเราครับ
**
กระบวนการทำเนยคือ
** การเอาครีมมาปั่นในถังปั่น จนมันเกิดการแยกระหว่างไขมันกับเวย์ เรียกว่าการ churning ตั้งแต่โบราณก็ใช้การปั่น แต่วิธีปั่นมันต่างไปเท่านั้นครับ จากปั่นมือ มาเป็นปั่นเครื่อง รสชาติของเนยก็ขึ้นอยู่กับวิธีทำต่างๆ ตั้งแต่โบราณคือนมดิบ, นมที่มีการ culture หรือ ใส่จุลินทรีย์ไปหมักก่อนจะนำมาปั่น เพื่อกลิ่นและรส ปัจจุบันก็อาจมีการพาสเจอร์ไรส์เพราะบางประเทศบังคับว่าต้องพาสเจอร์ไรส์
วันนี้เรามาดูแบบง่ายๆตามที่บอกไว้ข้างบน เราแค่เอาวิปครีม ใส่โถปั่นแล้วก็ให้มันปั่นไปเรื่อยๆ แค่นี้ก็ได้เนยแล้วครับ สำหรับคนที่ทำขนมน่าจะเคยเจอเหตุการณ์ตีวิปนานเกินไปจนจับก้อนแข็ง ถ้าคุณตีต่อไปอีกนั่นละครับ ไอ้เจ้าครีมแข็งนั้นจะกลายเป็นเนยในที่สุด เอาจริงๆการเหวี่ยงก็ได้นะครับ หลายคนเอาใส่ขวดแล้วเขย่า ใครอยากลองก็ลองได้นะ เมื่อยมือเชียว 5555 พอเราได้ก้อนเนยสดๆแล้ว เราก็เอามาใส่ลงในน้ำเย็นจัด ความเย็นจัดจะทำให้เนยสดๆนี้แข็งตัว แล้วเราก็จะปั้นก้อนปั้นรูปทรงให้เก็บง่ายๆได้ ที่นิยมก็ทรงหมูยอ เพราะตัดใช้ง่ายดีครับ
**เรามาดูคลิปที่ผมเคยทำกันครับ จะเห็นภาพว่า ครีมกลายเป็นเนย มันยังไง ** https://youtu.be/bzo7V9n2cxc?si=PsaldIxgKqpiBXgb
ทีนี้เราก็ได้เนยเอาไว้ใช้เองสบายๆละ ใครที่มีนมดิบอยู่แล้วกลัวกินไม่ทัน ก็มีวิธีเพิ่มนิดนึงครับคือ ใส่โถทรงสูงหน่อย เอานมดิบแช่ตู้เย็นราวๆ 18ชั่วโมงขึ้นไป จนมันเริ่มแยกชั้นกัน ความเย็นจะทำให้ไขมันจับตัว มองแล้วคล้ายหัวกะทิ หางกะทิ แล้วเราก็เลือกตักส่วนข้นๆส้วนจับก้อน เอามาใช้แทนครีม วิธีสังเกตุก็ดูความใสของนมเอาครับ ส่วนไขมันจะข้นๆหน่อย พอเริ่มไขมันน้อยก็จะใสครับ ส่วนที่เหลือที่ใสหน่อย นั่นละครับ นมไขมันต่ำ 55555 เอาไปชงกาแฟหรือดื่มได้ต่อไม่มีปัญหาอะไร
**
ทีนี้ กี (ghee) คืออะไร
** กี คือ เนยใส เป็นที่นิยมในอินเดียมากๆ เขาเอามาใช้เป็นน้ำมันในการทำอาหาร ชงเครื่องดื่ม ได้สารพัดอย่างตามที่น้ำมันจะทำได้ จุดเกิดควันสูง ทำให้เกิดการไหม้ ได้ยากกว่าเนยหลายเท่า
วิธีทำกี ก็ง่ายมากๆ แค่เอาเนยมาตั้งเตาด้วยไฟอ่อนๆ อ่อนมากๆนะครับ เพราะถ้าแรงไปนิดเดียว เนยจะไหม้ทันที เราก็กวนเนยไปเรื่อยๆ ความร้อนอ่อนๆที่ต้มเนยนี้มันคือกระบวนการทำให้น้ำระเหยออกไป จนเริ่มเห็นน้ำมันใสๆ เริ่มเห็นการแยกชั้นอีกครั้งนึง ซึ่งไอ้ที่แยกมานี่ละครับ เราเรียกว่า เนื้อนม หรือ solid milk เท่ากับว่าเราแยกองค์ประกอบของเนยออกไปได้ดังนี้ 1.น้ำระเหยไปในอากาศ 2.เนื้อนมแข็งๆคาอยู่ในหม้อ 3.ไขมันเนยใสๆ คาอยู่ในหม้อ
สิ่งที่เราเอามาใช้ก็คือ ไขมันเนย กรอกใส่ขวดหรือกระปุกก็ตามสะดวกใช้ครับ แช่ตู้เย็นเอาไว้ก็ได้ หรือถ้าใช้บ่อย อยู่นอกตู้เย็นก็ได้พักใหญ่ๆเลย เพราะมันไม่มีอะไรให้เสีย เพียงแค่มันจะซับกลิ่นสภาพแวดล้อมได้เก่งหน่อย
ส่วนเนื้อนมเอาไปคลุกน้ำตาลอร่อยครับ 555555
เรามาดูคลิปการทำกี กันครับ ตัวนี้ผมใช้เนยที่ขายทั่วไปพราะตอนนั้นผมทำการทดลอง ให้คนคีโตเห็นว่า อย่าไปอะไรกับเนยมาก ทุกตัวมีเนื้อนมหมดและเนื้อนมเป็นคาร์บ ที่สำคัญเนยที่คีโตนิยมใช้เหลือเนื้อนมมากกว่าเนยที่ราคาถูกกว่าอีก เพราะเนื้อนมคือตัวที่ทำให้เนยมีความละมุนลิ้น ส่วนไขมันเนยคือตัวที่ส่งกลิ่นหอมๆ ลองไปดูคลิปกันครับ
https://youtu.be/HFvvIjhZ6h0?si=KkqoZFN3Mx1lTTul
ทีนี้ของแถม ที่บอกว่าต้มกี ต้องระวังไหม้ จำได้ใช่ไหมครับ ในสายเบเกอรี่ เรามีสิ่งที่เรียกว่า บราวบัทเตอร์ (brown butter) คือการเล่นเสี่ยงอย่างนึงคือ ต้มกี ให้เกินจุดพอดี แต่ไม่เกินไปจนไหม้ เราจะได้เนยใสสีน้ำตาลอ่อน มีกลิ่นหอมคาราเมล ตัวนี้นิยมใช้ทำขนมเพิ่มกลิ่นหอมกว่าการใช้เนยปกติหลายเท่า แถมเป็นกลิ่นหอมหวาน ที่ทำให้ขนมไฮโซขึ้นมาก เอาไปชงกาแฟก็หอมครับผมทำบ่อย
siamstr #pirateketo
-
 @ f3b691eb:aa9a5c31
2024-03-08 19:48:13
@ f3b691eb:aa9a5c31
2024-03-08 19:48:13 -
 @ 3d599bf6:a0122cef
2024-04-24 09:26:09
@ 3d599bf6:a0122cef
2024-04-24 09:26:09This is just a test article.
-
 @ f3b691eb:aa9a5c31
2024-03-08 18:30:02
@ f3b691eb:aa9a5c31
2024-03-08 18:30:02 -
 @ f3b691eb:aa9a5c31
2024-03-08 15:45:19
@ f3b691eb:aa9a5c31
2024-03-08 15:45:19 -
 @ f3b691eb:aa9a5c31
2024-03-08 15:20:59
@ f3b691eb:aa9a5c31
2024-03-08 15:20:59 -
 @ f3b691eb:aa9a5c31
2024-03-08 14:53:08
@ f3b691eb:aa9a5c31
2024-03-08 14:53:08 -
 @ c6bef3ed:890586d5
2024-03-08 14:51:28
@ c6bef3ed:890586d5
2024-03-08 14:51:28 -
 @ 7175188c:6382a72c
2024-03-07 19:12:42
@ 7175188c:6382a72c
2024-03-07 19:12:42 -
 @ 73cee26b:072f3bb6
2024-03-02 14:30:09
@ 73cee26b:072f3bb6
2024-03-02 14:30:09Like every time it's XXX420 or XXXX69 or something?
-
 @ 0ec455f5:4c408fc7
2024-03-01 20:21:17
@ 0ec455f5:4c408fc7
2024-03-01 20:21:17 -
 @ 73cee26b:072f3bb6
2024-02-28 21:09:52
@ 73cee26b:072f3bb6
2024-02-28 21:09:52I haven't really been on nostr in a year or so, but playing around now it seems like there are WAY fewer zaps. There are some high-profile mega-zapped posts, but almost all posts and conversations are bereft of zaps. What happened? Recession?
-
 @ d91191e3:7efd4075
2024-02-27 14:39:20
@ d91191e3:7efd4075
2024-02-27 14:39:20Just want to test out highlighter.
-
 @ 0d6c8388:46488a33
2024-02-23 12:10:54
@ 0d6c8388:46488a33
2024-02-23 12:10:54this is a test I hope you get that by now
-
 @ f3df9bc0:a95119eb
2024-02-19 13:08:37
@ f3df9bc0:a95119eb
2024-02-19 13:08:37hello
-
 @ 10f074e8:46423506
2024-02-17 20:20:14
@ 10f074e8:46423506
2024-02-17 20:20:14test
-
 @ 10f074e8:46423506
2024-02-17 20:13:26
@ 10f074e8:46423506
2024-02-17 20:13:26asdf test test
-
 @ 83defd06:45cb69da
2024-02-13 17:05:15
@ 83defd06:45cb69da
2024-02-13 17:05:15testing
-
 @ 83defd06:45cb69da
2024-02-13 17:03:57
@ 83defd06:45cb69da
2024-02-13 17:03:57testing sorry
-
 @ 0f2955a6:2ad7991a
2024-02-12 23:23:59
@ 0f2955a6:2ad7991a
2024-02-12 23:23:59test test
-
 @ d19fec54:1e6c5495
2024-02-12 23:15:54
@ d19fec54:1e6c5495
2024-02-12 23:15:54test test
-
 @ d19fec54:1e6c5495
2024-02-12 22:43:48
@ d19fec54:1e6c5495
2024-02-12 22:43:48test
-
 @ babaf02c:049eee5d
2024-02-08 06:19:29
@ babaf02c:049eee5d
2024-02-08 06:19:29Introducing Amazon Cleaning, the trusted name in Smyrna cleaning service. We are committed to making your space shine, so you can sit back and relax. With our team of expert cleaners, you can trust that every nook and cranny will be thoroughly cleaned and sanitized to perfection. From residential homes to commercial spaces, we offer a wide range of cleaning services tailored to your specific needs. Whether it's a weekly, bi-weekly, or one-time cleaning, we've got you covered. Our attention to detail, professionalism, and use of eco-friendly products sets us apart from the rest. Experience the convenience and happiness of a spotless space with Amazon Cleaning today!
-
 @ 0d6c8388:46488a33
2024-02-02 14:01:23
@ 0d6c8388:46488a33
2024-02-02 14:01:23 -
 @ e42dd2a2:eeddb96f
2024-02-01 16:24:23
@ e42dd2a2:eeddb96f
2024-02-01 16:24:23after it for real this time
-
 @ e42dd2a2:eeddb96f
2024-02-01 16:22:27
@ e42dd2a2:eeddb96f
2024-02-01 16:22:27Lorem ipsum lorem ipsum
-
 @ e42dd2a2:eeddb96f
2024-02-01 16:20:37
@ e42dd2a2:eeddb96f
2024-02-01 16:20:37once again my friend
-
 @ 83defd06:45cb69da
2024-01-30 20:10:39
@ 83defd06:45cb69da
2024-01-30 20:10:39test test sorry
-
 @ 2863f394:275ed58d
2024-01-27 11:15:32
@ 2863f394:275ed58d
2024-01-27 11:15:32I setup a node or two...spent $400 each for incoming and outgoing and now I can't receive payments anymore. I basically lost $800 on this garbage.
-
 @ 676c0224:e641b6d6
2024-01-21 23:31:58
@ 676c0224:e641b6d6
2024-01-21 23:31:58testing testing
-
 @ 676c0224:e641b6d6
2024-01-21 23:21:21
@ 676c0224:e641b6d6
2024-01-21 23:21:21test test test test
-
 @ 676c0224:e641b6d6
2024-01-17 22:29:59
@ 676c0224:e641b6d6
2024-01-17 22:29:59testr testr
-
 @ 9bd40302:1aa99571
2023-12-11 16:27:48
@ 9bd40302:1aa99571
2023-12-11 16:27:48This is my first article in Nostr
-
 @ a023a5e8:ff29191d
2023-12-10 19:35:14
@ a023a5e8:ff29191d
2023-12-10 19:35:14 -
 @ 83defd06:45cb69da
2023-12-08 21:32:34
@ 83defd06:45cb69da
2023-12-08 21:32:34tester tester
-
 @ 83defd06:45cb69da
2023-12-04 14:47:04
@ 83defd06:45cb69da
2023-12-04 14:47:04Plz center this div for me sir
-
 @ 2863f394:275ed58d
2023-12-02 03:03:56
@ 2863f394:275ed58d
2023-12-02 03:03:56the docs at webln.guide don't say how to specify the recipient of a payment.
-
 @ 96c35a92:ec44c88e
2023-11-28 12:55:25
@ 96c35a92:ec44c88e
2023-11-28 12:55:25Testing @stackernews cross posting to Nostr
-
 @ 2863f394:275ed58d
2023-11-24 23:23:06
@ 2863f394:275ed58d
2023-11-24 23:23:06Like for sharing in a #zapathon or something.
-
 @ 83409ce4:a2f35500
2023-11-10 06:17:53
@ 83409ce4:a2f35500
2023-11-10 06:17:53焼き本音のテストです。
-
 @ 9ecbb0e7:06ab7c09
2023-11-05 07:57:18
@ 9ecbb0e7:06ab7c09
2023-11-05 07:57:18test
-
 @ 75bf2353:e1bfa895
2023-11-04 18:29:46
@ 75bf2353:e1bfa895
2023-11-04 18:29:46I'll award 100 sats to the first person that applies for this bounty just to test it out.
-
 @ 9ecbb0e7:06ab7c09
2023-11-03 06:14:28
@ 9ecbb0e7:06ab7c09
2023-11-03 06:14:28prueba
-
 @ 9ecbb0e7:06ab7c09
2023-10-17 06:35:46
@ 9ecbb0e7:06ab7c09
2023-10-17 06:35:46test de prueba
-
 @ 6389be64:ef439d32
2023-10-14 19:34:10
@ 6389be64:ef439d32
2023-10-14 19:34:10Testing . . . again.
-
 @ faa4cc0f:dcff8126
2023-10-14 16:52:14
@ faa4cc0f:dcff8126
2023-10-14 16:52:14ปล่อยผมไปที
-
 @ 9071d94a:6967c53b
2023-10-11 22:08:51
@ 9071d94a:6967c53b
2023-10-11 22:08:51Plz
-
 @ 8cb60e21:5f2deaea
2023-10-11 22:04:40
@ 8cb60e21:5f2deaea
2023-10-11 22:04:40Does this work?
-
 @ 83defd06:45cb69da
2023-10-11 21:52:35
@ 83defd06:45cb69da
2023-10-11 21:52:35Good evening
-
 @ 1f52b16e:0ab23c84
2023-09-16 19:51:56
@ 1f52b16e:0ab23c84
2023-09-16 19:51:56Originally posted March 2023 at 1f52b.xyz. Read there for sidenotes & references.\n\n---\n\n> Now the serpent was more subtil than any beast of the field which the Lord God had made. And he said unto the woman, Yea, hath God said, Ye shall not eat of every tree of the garden?\n>\n> Genesis 3:1\n\nBitcoin has NFTs now. They're called Ordinal Inscriptions, but what the heck is an Ordinal and what's an Inscription? And why should you care? The arrival of NFTs in the Bitcoin universe has caused a fair amount of drama. Ordinal enjoyers welcome the shiny new hotness, while many others see a serious attack on Bitcoin -- guzzling up blockspace that should have been used by normal financial transactions, miners ripping massive four-meg'er blocks full of spam; and an attack on the very fungibility of Bitcoin.\n\nOrd, wallet software that runs alongside Bitcoin Core was released to the world in January 2023. Its creator, Casey Rodarmor, the inventor of Inscriptions and Ordinal theory has conceived of a way to use, or exploit Bitcoin's Taproot script, enabling co-conspirators to store a large amount of arbitrary data within otherwise normal transactions created using ord. It uses a construction called an envelope -- a piece of code within the Taproot witness part of a transaction that all the nodes of the network will skip over when validating it, but which contains stuff -- arbitrary data that can be extracted by anyone who knows where to look. As this simply uses existing opcodes and an otherwise standard Taproot transaction, Inscriptions have debuted onto the Bitcoin mainnet with zero code changes to Bitcoin Core required. No developer consensus nor permission was needed nor asked to unleash ord.\n\n> Ordinal theory does not require a sidechain or token aside from Bitcoin, and can be used without any changes to the Bitcoin network. It works right now.\n>\n> Ordinals.com\n\nThis is the first piece of genius. The envelope construct is really simple, one of those things that in hindsight should have been obvious. There's nothing really new or hard to wrap your head-around about it. And there's not really anything that can be done to stop it. The consensus rules allow it, so it is.\n\nWhile there are many things one could use near-arbitrary, permanent, globally distributed & censorship-resistant storage for, it probably isn't shocking to hear that much of the content already inscribed on-chain are the same endearing monkey JPEGs and dickbutts we've know and love from the shitcoin NFT craze.\n\n
 \n\nStoring stuff on the Bitcoin blockchain that isn't merely a financial transaction is nothing new. Famously, the Bitcoin Genesis block carries the headline "The Times 03/Jan/2009 Chancellor on brink of second bailout for banks" in its coinbase transaction. Since the inclusion of that piece of text in the very first transaction in the very first block, thousands upon thousands of other non-financial pieces of data have been permanently stored on the chain.\n\nThe methods for achieving this have evolved over the years, and some of them really weren't great -- causing problems for nodes by consuming precious UTXO set storage, and some using fake unspendable addresses as the storage mechanism, resulting in permanently burned coins. This mess was addressed by Bitcoin-Core begrudgingly introducing the
\n\nStoring stuff on the Bitcoin blockchain that isn't merely a financial transaction is nothing new. Famously, the Bitcoin Genesis block carries the headline "The Times 03/Jan/2009 Chancellor on brink of second bailout for banks" in its coinbase transaction. Since the inclusion of that piece of text in the very first transaction in the very first block, thousands upon thousands of other non-financial pieces of data have been permanently stored on the chain.\n\nThe methods for achieving this have evolved over the years, and some of them really weren't great -- causing problems for nodes by consuming precious UTXO set storage, and some using fake unspendable addresses as the storage mechanism, resulting in permanently burned coins. This mess was addressed by Bitcoin-Core begrudgingly introducing the OP_RETURNconstruction, and that seemingly resolved the question of storage on chain. Prior to the conception of Ordinal Inscriptions, usingOP_RETURNhas been by-far the most common way to store stuff -- at times, contributing a significant share of all transaction volume and fees, though in recent years usage has steadily declined as the main volume drivers Omni and Veriblock have lost adoption.\n\n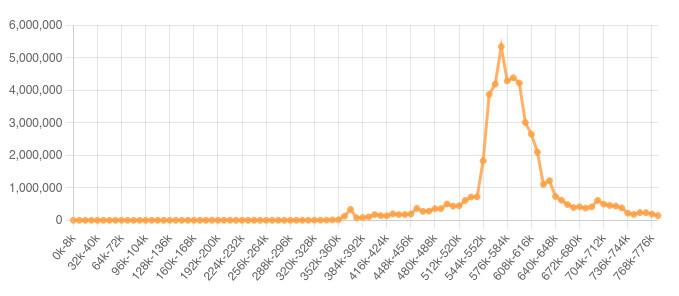 \n\nAbove:
\n\nAbove: OP_RETURNusage statistics by block, showing sharp peak then decline. Via opreturn.org\n\nBut,OP_RETURNis limited to 80 bytes of data. That's workable for short snippets of text, but you can't cram much else in there. That limit also gives a pretty clear indication of the core dev’s feelings about storing data on chain -- don’t. Alas, because of a minor rule change introduced without much fanfare as part of the Taproot upgrade, the limit to script sizes that applied to SegWit was removed. This means Inscriptions are only capped in size by the blocksize limit of 4MB itself (or 4 million weight units, to be exact). An Inscription can be the only non-coinbase transaction in a block, filling the entire thing up itself. That's a big deal -- and yes, this has already happened (well, nearly).\n\n \n\nAverage blocks in an Ordinal world are indeed bigger than the ~1.4MB we'd grown accustomed to since the SegWit upgrade raised the limit from a hard 1MB. Bigger blocks increase the rate at which network nodes fill up their storage, and the fallout of the 2017 blocksize wars should be all that was needed to demonstrate how thermonuclear the question of block size is. Nevertheless, those mad at Ordinals for increasing the blockchain's growth rate are in truth angry that the possible-in-theory since SegWit and Taproot activated has now become reality. The block-size limit was increased to 4MB back then, not in January 2023 when Casey released
\n\nAverage blocks in an Ordinal world are indeed bigger than the ~1.4MB we'd grown accustomed to since the SegWit upgrade raised the limit from a hard 1MB. Bigger blocks increase the rate at which network nodes fill up their storage, and the fallout of the 2017 blocksize wars should be all that was needed to demonstrate how thermonuclear the question of block size is. Nevertheless, those mad at Ordinals for increasing the blockchain's growth rate are in truth angry that the possible-in-theory since SegWit and Taproot activated has now become reality. The block-size limit was increased to 4MB back then, not in January 2023 when Casey released ordto the world. Blocks are meant to be full. If you hate Ordinals because they are filling juicy 4MB blocks, look to Taproot and SegWit for original sin. In a weird quirk, Inscriptions actually make blocks smaller for anyone running a pre-SegWit node, as the non-witness portion of the block is much smaller.\n\nWhat’s more, in many ways it doesn’t matter what anyone thinks about Inscriptions. These are valid Bitcoin transactions so there’s next to nothing that can be done to stop them -- that is after-all the point of Bitcoin. You can run a node with core-dev Luke Dashjr’s 'ordisrespector' patch that will filter unconfirmed Inscriptions out of your mempool, but unless the vast majority of Bitcoin node runners do this (spoiler: they haven't), it’s a pointless exercise as Inscription transactions will still find their way to willing miners.\n\n> #Bitcoin node patch (HACKY, UNTESTED) to filter out "ord" spam.\n>\n> NOT a protocol change or softfork/hardfork, just a harmless (if it works right) spam filter.\n>\n> (Also a quick hack and NOT suitable for opening a PR to Core -- please write a proper fix for that)\n>\n> Luke Dashjr on Twitter\n\nMore drastic action than changing nodes' mempool policy could be taken, such as a fork that tightened the rules back down again to limit the max script size for Taproot. Or, make any script that contains unreachable code (as envelopes do) invalid. But forking Bitcoin just to censor a specific use of it would be an act of self-defeat nearly as stupid and catastrophically damaging to Bitcoin's core tenets as Ethereum's DAO fork and bailout of 2016. It would betray the fundamental ideals that underpin Bitcoin and make a mockery of its philosophy. Mostly for this reason, because such an effort would likely meet fierce resistance and result in a permanent chain split; and presumably also because someone had a 'sanctioned' use of large tapscripts in mind, there have been no serious proposals to do this.\n\nThis is a second piece of perhaps unwitting genius -- Ordinal Inscriptions are again proof that no single group, including the core developers, control the protocol. They prove that Bitcoin is nearly impossible to censor; that it is money for enemies. Miners are incentivised to mine blocks containing Inscriptions given they pay a fee just as any other transaction does. Users make these transactions. So, Inscriptions continue to make it into blocks. This is nice little lesson on one of the strengths of Bitcoin -- incentive-aligned systems are stable and resist attack.\n\nIt goes without saying that Inscription transactions are big -- that's kinda the whole point. This also means that they're not economically dense at all. A normal SegWit transaction can move hundreds of bitcoin worth billions of dollars in under 200 bytes, paying a fairly small fee. For Inscriptions, the value moving through transactions is much less contained in the quantity of sats moving, and more in the subjective and speculative value of the artwork in the kilobyte or megabyte sized witness data -- but the Bitcoin network doesn't care, and so artists and buyers must pay fees for what they use and can only hope to later make a return on their investment.\n\nSo it follows that the criticism of Inscriptions claiming that they are crowding other economic activity out of blocks is unfounded. Put it this way -- a Lightning channel open transaction between two large nodes is the on chain footprint of a fast payments network that is expected to scale to processing thousands of transactions per second and moving mountains of value every minute. That kind of economic actor can afford a fee of hundreds or thousands of sats per byte and outcompete practically everyone else in the fee market, a rate still way higher than current next-block rates. Rates that high would make even a modestly sized Inscription cost more than a whole bitcoin in fees. Inscriptions are setting a fee floor and avoiding unfilled blocks, but by no means are they crowding everyone else out -- and when Lightning really takes off, the opposite will be true.\n\nI don't subscribe to the argument that Inscriptions will particularly help to solve the long-term Bitcoin security budget -- that miners will need to make the entirely of their profit from fees once the block reward reduces to zero. Yes, any kind of adoption helps, but Inscriptions probably don't help any more than that. What really matters for the security budget is that the sum total of the fees paid to miners can purchase a large amount of energy, not that the fee rate needs to rise. There are only ever going to be 2.1 quadrillion satoshis in existence, which in a hyperbitcoinised world could mean a fee of 1 sat/vByte is not nothing in monetary terms. By comparison, there are currently around 2.1 quadrillion US¢ in existence. But that's a tangent for another time.\n\n> I think we’re going to see things like Inscriptions and Ordinals be the next biggest thing that happens in Bitcoin, there is a massive amount of demand for that stuff. Me liking or not liking it is irrelevant. The shitcoiners are running now Bitcoin nodes and full nodes cos they want their Inscriptions there. That’s an interesting funnel for Bitcoin.\n>\n> NVK on the Stephan Livera Podcast - SLP459\n\n\n> "you can't stop them" well ofc! bitcoin is designed to be censor resistant. doesn't stop us mildly commenting on the sheer waste and stupidity of an encoding. at least do something efficient. otherwise it's another proof of consumption of block-space thingy.\n>\n> Adam Back on Twitter\n\nIn spite of all this controversy and squabbling amongst friendly bitcoiners, I hope we all can take a moment to appreciate a certain deliciousness here: Bitcoin accidentally has a NFT scheme that’s just better than the incumbent NFTs of the shitcoin world. Do you actually understand how smart-contract based NFTs work? The contract code is highly complex, written in a Turing-complete language that's much harder to reason about than Bitcoin script's simple stack, and often unaudited by buyers, with various standards in use across different collections and mints. To boot, you also need to understand the workings of which ever shitcoin chain it transacted on, and what their patron 'foundation' and VCs are up to. In truth, I don't fully understand how it all works despite putting in some effort. In contrast, it took about two minutes to grok how envelopes work, and another two to see how Ordinals facilitate the transfer of Inscriptions between current and new owner. I'm sure someone could argue existing NFTs are fine or even great, but the comparative simplicity of Inscriptions speaks for itself.\n\n> My primary goal is protecting our community. If it has a token that isn’t bitcoin, it is not bitcoin.\n>\n> Shitcoiners have been trying to rip normal people off with rube goldberg machines that don’t work and nobody understands.\n> \n> Casey Rodarmor on Twitter\n\n\nWorse still, the majority of NFTs are merely a claim to a small piece of on-chain metadata that contains a URL as an indirect reference to an image that lives elsewhere on the internet, somewhere much less permanent; like IPFS or an Amazon S3 bucket. If your Monkey JPEG isn’t on chain, do you really own it? What do you actually own? Ordinal Inscriptions are permanently burned onto the oldest, most secure chain there is. This is just better.\n\nOrdinals aim to provide a farer, safer system for creating and trading digital artifacts where the system is simple enough to be understood so that all buyers and artists know exactly what they're doing and dealing with. These are NFTs, but more ethical. No rugpulls with Ordinals.\n\nSome of the crypto bros have already realised the big upgrade that Inscriptions present. \n\n> I want the shitcoiners to come to us and assimilate into our culture\n>\n> Casey on the Bitcoin Review Podcast BR024\n\nEnter the "Teleburn". NFTs from other chains can be inscribed onto Bitcoin, and then destroyed, burned permanently from the old chain. You can see the appeal -- an NFT on Bitcoin is better than one on Ethereum or Solana or wherever. Burning a Bored Ape attracts attention and headlines. There's the allure of being first.\n\nI have to admire the sheer audacity of the Teleburn. The upstart alternative to altcoin NFTs goes straight for the jugular with Teleburns, not seeking to join the NFT ecosystem but supplant it. While fears that Ordinals are an attack on Bitcoin are overblown if not entirely FUD, Teleburns are an attack on the entire shitcoin NFT ecosystem.\n\n> "Essentially throwing a Lamborghini into a trash compactor–It’s kind of fun," Williams told Decrypt. "Whether putting bloated JPEGs on Bitcoin’s base chain is smart or not is a whole ‘nother discussion, but I think it’s going to be a lot of fun seeing how it plays out."\n>\n> Bored Ape Owner Burns $169K NFT to Move It From Ethereum to Bitcoin (Decrypt)\n\nPrima-facie, Inscriptions might merely be the new fun thing to mess with for the crypto and web3 inclined, a new goldrush where some of them might make a ton of money while it lasts. But what Casey has done with ord is trick a bunch of crypto bros into running full, synced Bitcoin nodes. You have to, if you want to use ord and inscribe something, a piece of genius design rather than a compromise limitation of some new and unpolished software.\n\nHow may of them were already running a full Ethereum node? Given you kinda need a stonking 30TB or more of free disk space to do so, I'd guess literally none of them.\n\nThere’s a chance that some of them might get it and catch the Bitcoiner bug.\n\n> It really is like a needle exchange program for degens. We bring them over to like a safer place and give them a dime bag of sats to get them hooked. Like, it’s hilarious!\n> \n> Rijndaael, Ord contributor on the Bitcoin Review Podcast BR024\n\nYou may notice we've spent most of our time so far talking about Inscriptions, but Ordinal sats, or more exactly "Ordinal Theory" has courted its own controversy. (A quick clarification -- Inscriptions attach a digital artefact, like a JPEG to a sat, and then Ordinals are how we track ownership. Despite this technicality, the whole thing lumped together is usually just called "Ordinals".)\n\nPart of this backlash might be confusion. Ordinal theory is entirely opt-in, and is literally just a convenient schema, or lens to view Bitcoin through. We socially agree on this theory that allows us to give every satoshi a unique number, just as banknotes have serials. It's a lens through which you get an interesting and useful view of the Bitcoin system, but nothing more profound than that. If you hate it, cool, just ignore it.\n\nThe reason that Ordinal Theory arrived at the same time as Inscriptions is that it answers the follow-up question "how do I transfer ownership of an Inscription?" The answer is straightforward if we agree on Ordinal Theory, which then allows us to track satoshis from their genesis in the block that first produced them, through every transaction they are involved in. Doing this, it is then easy to see who the current owner of a sat that was used in an Inscription transaction -- an 'inscribed sat' -- is.\n\n> Ordinal Theory imbues satoshis with numismatic value, allowing them to be collected and traded as curios.\n> \n> Ordinals.com\n\nPredictably, the notion that sats can be uniquely identified, tracked through transactions, and made 'special' by being Inscribed triggered a hostile reaction from many Bitcoiners. It is critical to the functioning of money that it is fungible -- one bitcoin over here needs to have precisely the same exchange value as another over there.\n\nThis is probably a healthy response -- a concern that fungibility has in some real sense been damaged. But all that Ordinal Theory is doing is following the existing rules of Bitcoin, where everything in the ledger and supply schedule has a strict order, and adding a few conventions to complete the missing pieces of the picture. If that is all it takes to break the fungibility of Bitcoin, then it was never really fungible.\n\nOrdinal Theory does not at all reduce the privacy of coinjoins. I'm not sure how else to argue against that claim other than to say its proponents have simply misunderstood Ordinal Theory, or misunderstood coinjoins. A chain analysis company or government agency could easily have come up with a similar scheme themselves, and might already have done so -- but you still can't tell who was on the input nor output side of a transaction any more than you previously could.\n\nAll this does bring, in addition to the ability to trade Inscriptions like NFTs, is numismatism. That is, within Ordinal Theory, some sats are more interesting than others. Sats from Satoshi blocks, and rare & important events in Bitcoin's history like halvings, difficulty adjustments, fork activation blocks and Exchange hacks can be all identified and then collected by people that value such things.\n\nSo now we have numismatism on Bitcoin. Coin and stamp collectors do not threaten the fungibility nor utility of Fiat monies, and nor will they now that they’re here. The additional value that collectors may ascribe to a specific sat doesn't stop someone that doesn't care from using it to buy coffee, in the some way that your Barista probably won't notice or care if you pay for coffee with a dollar bill that has a nice round serial number, and certainly won't offer you a discount.\n\nThis also doesn't mean that "bad" satoshis are any more encumbered than they already were. OFAC and the FBI don't need Ordinal Theory to track transactions and blacklist addresses and UTXOs. That this was already possible is the reason conjoins and other privacy enhancing tech has been available for many years.\n\nBig and controversial moves in Bitcoin increasingly lead to calls for 'ossification' -- a growing conservatism against any change to consensus. Very clever upgrades like Taproot always promise great new things and fixes for nagging problems. But that latest upgrade to Bitcoin unintentionally enabled Inscriptions, something many Taproot proponents thoroughly dislike. It's reasonable to wonder if there are other unanticipated uses for it or earlier upgrades still lingering and waiting to be discovered. Some of these could genuinely be harmful to Bitcoin, and there's always a risk that making a change that has catastrophic unrecoverable consequences, however unlikely. Taproot is very clever, but it is also very complicated and hard to fully understand -- the club of people who do is small. What we have now works well, change can be dangerous. It should become increasingly onerous to introduce new things into Bitcoin, to the point that eventually the only changes to core will be non-consensus changes, like bug fixes and performance enhancements that make Bitcoin as currently instantiated stronger.\n\nIt can take a lot of time to come up with the best solution to an extant problem. Much of the argument in favour of big blocks in the 2015-2017 blocksize war was that there was no other way to scale Bitcoin into a global payments system that would be capable of VISA and Mastercard volumes. Then, Lightning happened, presenting a much better alternative to dumb big blocks.\n\nThe next thing in the pipeline is Vaults & Covenants. In the wake of Taproot's unintentional enabling of Inscriptions, it would be healthy for us to take our time ensuring these new features behave as intended and don't bring any surprises. Not to say that these proposals don't already receive intense scrutiny and testing, yet Inscriptions gifted us a safe 'failure' case for perhaps 'too clever' changes to consensus that have been merged. It is incredibly difficult to think of something no-one has yet though of. Once we’ve activated a consensus change, it’s nearly impossible to put the cat back in the bag and walk back. We should be increasingly sceptical of any consensus rule change and be increasingly rigourous in evaluating it for unintended consequences and unintended use-cases. The burden of "do we really need this" should continue to get higher and higher.\n\nThe final piece that Inscriptions bring to Bitcoin is the thing we may come to be most thankful for. There are those that argue "code is speech", and thus Bitcoin and its network are protected under the First Amendment of the US Constitution. That argument is perhaps contestable, but that literal art and words are speech is not -- and now those are being etched directly into Bitcoin's blocks.\n\nBitcoin is how more clearly than ever a venue for freedom of expression as protected by the First Amendment. Attempts to censor or restrict the use of Bitcoin by the US government could be legally challenged as a violation of this right, perhaps leaning on Inscriptions to make this case. Of course other countries have different rights & weaker freedoms of speech, with illiberal codes where the freedom to say what you wish could make Bitcoin more of a pariah not less -- but it is perhaps in the United States were Bitcoin's continuing success is most important, as it is the hegemony of the US dollar that it seeks to supersede.\n\n---\n\n> Don't think about making art just get it done.\n>\n> Let everyone else decide if it's good or bad, whether they love it or hate it.\n>\n> While they are deciding, make even more art.\n>\n> Andy Warhol\n> \n> Inscription #5\n -
 @ 6efb74e6:41285536
2023-09-09 15:15:49
@ 6efb74e6:41285536
2023-09-09 15:15:49proofofwork: 10 minutes \n\nYIELD: approx 2 1/2 cups.\n\nINGREDIENTS: \n\n1 cup parsley, washed and finely chopped \n\n1 cup cilantro, washed and finely chopped\n\n5 ea (1 teaspoon) garlic cloves\n\n3 Tablespoons fresh oregano (2 tsp if using dried)\n\n1 teaspoon fresh chilli or chilli flakes\n\n1 teaspoon ground cumin, lightly toasted\n\n2 Tablespoons quality red wine vinegar\n\n1/2 cup extra-virgin olive oil\n\n1 tablespoon lime juice\n\n1/2 teaspoon salt \n\n1/2 teaspoon black pepper \n\n\nMETHOD:\n\n1. Pick and wash all the herbs, drying them as much as possible with a salad spinner or a tea towel.\n2. Place all the chimichurri ingredients except the oil in a large bowl and mix them together well. \n3. Add the oil until you reach the consistency you desire. If you are using it as a marinade then you will probably want slightly less oil.\n4. When using as a marinade, coat your meat before grilling and refrigerate for at least 2-3 hours. \n\nCheck the seasoning and adjust it as you like.\n\n#chefstr, #foodstr, #yumstr, #grownostr, #homemade\n
-
 @ 1d22e00c:50e00d0e
2024-04-24 04:26:44
@ 1d22e00c:50e00d0e
2024-04-24 04:26:44Hey everyone and welcome to Refinery Life Australia.
This series is based on the Beatitudes, found in the beginning of the Sermon on the Mount.
Today we are discussing, The Poverty That Possesses.
Text
Matthew 5:3 NKJV
3 “Blessed are the poor in spirit, For theirs is the kingdom of heaven.
Scripture Reading
2 Corinthians 8:1-9 NKJV
Excel in Giving
1 Moreover, brethren, we make known to you the grace of God bestowed on the churches of Macedonia:
2 that in a great trial of affliction the abundance of their joy and their deep poverty abounded in the riches of their liberality.
3 For I bear witness that according to their ability, yes, and beyond their ability, they were freely willing,
4 imploring us with much urgency [a]that we would receive the gift and the fellowship of the ministering to the saints.
5 And not only as we had hoped, but they first gave themselves to the Lord, and then to us by the will of God.
6 So we urged Titus, that as he had begun, so he would also complete this grace in you as well.
7 But as you abound in everything—in faith, in speech, in knowledge, in all diligence, and in your love for us—see that you abound in this grace also.
Christ Our Pattern
8 I speak not by commandment, but I am testing the sincerity of your love by the diligence of others.
9 For you know the grace of our Lord Jesus Christ, that though He was rich, yet for your sakes He became poor, that you through His poverty might become rich.
Prayer
Father, we thank You for adopting us as your children.
With eyes wide open to Your mercies, we come to dedicate ourselves to you afresh.
Help us to use our talents and testimony that others may know Christ.
As be bring our tithes and offerings, we pray Your blessings upon them.
Help us meet the expenses of the ministry of this church and engage in ministries to the outer most ends of the earth.
In Jesus name we pray.
Amen.
Introduction.
The person who is truly poor in spirit is blessed because such poverty enables that person to possess the supreme possession of all, “the kingdom of heaven.”
For our sakes, Jesus set the example in 2 Corinthians 8:9, For you know the grace of our Lord Jesus Christ, that though He was rich, yet for your sakes He became poor, that you through His poverty might become rich.
Poverty of spirit is the first character trait Jesus wants in His followers, the subjects of His kingdom.
It is a trait that carries its own reward, “theirs is the kingdom of heaven.”
Note the tenses here carefully, “Blessed are the poor in spirit,” not “have been,” or “ shall be,” but “are.”
Two questions about his beatitude call for an answer.
- What is poverty of spirit?
Jesus said that the ones who are poor in spirit are blessed.
How so?
What does He mean?
Let’s consider the answer from two points of view.
Firstly negatively.
Poverty of spirit does not mean poverty of possessions.
It is true that earthly poverty does sometimes produce conditions in which Christian virtues might thrive.
It is also true that the Bible warns us against “the cares of this world and the deceitfulness of riches” because of their power to distract us from the desire for heaven’s treasure.
But happiness is a matter of character, not conditions.
It issues from the rightness of our hearts, the relationships of our lives, and not from external conditions.
A person may be a millionaire and yet be poor in spirit.
Someone could be penniless but also proud and arrogant.
Poverty of spirit does not mean poverty of native endowment.
No life was ever richer that Jesus’ life, yet He was poor in spirit.
Poverty of spirit does not mean poverty of spiritual life in the sense of being feeble and neutral in our life.
Jesus came to bring the abundant life.
He had patience with those of little faith, those weak in spirit, and those impetuous in actions.
But He wanted to help them grow, to be of great faith, to be of strong convictions.
Poverty of spirit does not mean pretension of humility.
Some are great at self depreciation.
Jesus had no patience with the sort of person that is always saying “I am nothing and nobody and not worth your attention.”
Often deep down in their hearts, they are desirous of people knowing them in the marketplace and being the proudest of the proud.
The pride that apes humility is more detestable than the pride that casts of all disguise.
The second point of view is the positive.
What then is this poverty of spirit that Jesus called blessed?
Poverty of spirit is that quality of spirit that accurately perceives that man, as he is, has no virtue inherent in himself, that each gift and each grace of the spirit comes from God.
When we see how completely dispossessed of virtue and grace and righteousness we are in ourselves, pride, self esteem, and self righteousness must fall away.
Then we see how rebellious against God and His righteousness our wills have been, we want to cry our with Paul, “Wretched man that I am!” (Romans 7:24)
Poverty of spirit is the realisation that spiritually we are dispossessed, bankrupt, and without merit of our own.
Poverty of spirit is that quality of spirit that recognises that, apart from God, man is forever incomplete, and that the true centre of life is God.
The world has little time and no admiration at all for such a person.
Rather, it admires the self sufficient man, the self confident man, the so called self made man, the man who feels he is complete within himself.
The Greek philosopher Plato, discussing the good man, the happy man, places one condition upon him, he must be self sufficient.
Can you imagine standing before the Lord and expecting to enter heaven but also saying you were self sufficient?
Poverty of spirit is that quality of spirit that intensely desires that God will supply the true needs of the soul.
Jesus told a story of “two men” who “went up to the temple to pray.”
One, a Pharisee, did not actually pray.
Instead, he gave God a recital of his qualities and virtues.
He was self righteous, self satisfied.
This is exactly what poverty of spirit is not.
The other man, a publican, was so conscious of his need, so full of the sense of his own shortcomings, he would not even lift his head.
Yet, so desirous was he of God’s blessings that he cried out, “God be merciful to me a sinner.”
This is poverty of spirit.
2. How does this poverty of spirit bless us?
In what sense is it true that the poor in spirit are happy in the blessings of possessing the kingdom?
Here are five links in a chain that must not be broken.
Poverty of spirit causes us to seek in Christ the grace we need.
We need not mere conviction of sin, for conviction does not always lead to repentance and conversion.
Poverty of spirit is that appraisal of our lack on the one hand and of our sins on the other that cause a person to seek salvation.
Poverty of spirit conditions us for receiving the gift of God.
All of the prophets have realised this.
Isaiah said in Isaiah 57:15, For thus says the High and Lofty One Who inhabits eternity, whose name is Holy: “I dwell in the high and holy place, With him who has a contrite and humble spirit, To revive the spirit of the humble, And to revive the heart of the contrite ones.
David said in Psalm 51:17, The sacrifices of God are a broken spirit, A broken and a contrite heart— These, O God, You will not despise.
Poverty of spirit releases the saving grace of God upon us.
This is our only hope.
This is effective only when we empty our hearts of self and throw ourselves like broken vessels on His mercy.
Poverty of spirit fits us for service in the kingdom.
God loves to use the life that keeps self out of sight and honours only Him.
Poverty of spirit opens the eyes of the heart on the broad horizons of heavens possessions.
The vision says, “You are a child of the king. These things are yours.”
Conclusion.
Let’s test ourselves.
Let each of us ask, “Am I poor in spirit, or am I self satisfied, self righteous, and arrogant?”
Until next time
Stay in the Blessings
I really want to encourage you to be diligent with your Bible study time, because God has so much more for us than we can get from just going to church once or twice a week and hearing someone else talk about the Word.
When you spend time with God, your life will change in amazing ways, because God is a Redeemer. Theres nothing thats too hard for Him, and He can make you whole, spirit, soul and body!
You’re important to God, and you’re important to us at The Refinery.
When it comes to prayer, we believe that God wants to meet your needs and reveal His promises to you.
So whatever you’re concerned about and need prayer for we want to be here for you! Or even if you just want to say Hi, you can contact us at www.refinerylife.org
2024 IS A YEAR OF DECISIONS AND OPEN DOORS
© www.refinerylife.org 2013-2024 All rights reserved. Except as permitted under the Australian Copyright Act 1968, no part of this Article may be reproduced, stored in a retrieval system, communicated or transmitted in any form or by any means without the prior written permission.
This episode is brought to you by Refinery Life Australia:
If you enjoy The Refinery Life Radio Podcast you can help support The Refinery by doing the following:
Sow an offering: Bitcoin: bc1qqh6720t2zagj72dyfj348az698tdut3hlecaj4
Online: https://www.refinerylife.org/donate/
If you do send an offering then please email us so that we can say thank you
Subscribe on iTunes | Spotify | YouTube | TuneIn | Rumble | Flare | Zap.Stream | Fountain |
Share The Refinery with your friends and family
Subscribe to the newsletter on www.refinerylife.org
Follow The Refinery on Twitter | Nostr | Instagram | Fountain |