-
 @ fd208ee8:0fd927c1
2024-11-08 10:27:40
@ fd208ee8:0fd927c1
2024-11-08 10:27:40You have no idea
I regularly read comments from people, on here, wondering how it's possible to marry -- or even simply be friends! -- with someone who doesn't agree with you on politics. I see this sentiment expressed quite often, usually in the context of Bitcoin, or whatever pig is currently being chased through the village, as they say around here.

It seems rather sensible, but I don't think it's as hard, as people make it out to be. Further, I think it's a dangerous precondition to set, for your interpersonal relationships, because the political field is constantly in flux. If you determine who you will love, by their opinions, do you stop loving them if their opinions change, or if the opinions they have become irrelevant and a new set of opinions are needed -- and their new ones don't match your new ones? We could see this happen to relationships en masse, during the Covid Era, and I think it happens every day, in a slow grind toward the disintegration of interpersonal discourse.
I suspect many people do stop loving, at that point, as they never really loved the other person for their own sake, they loved the other person because they thought the other person was exactly like they are. But no two people are alike, and the longer you are in a relationship with someone else, the more the initial giddiness wears off and the trials and tribulations add up, the more you notice how very different you actually are. This is the point, where best friends and romantic couples say, We just grew apart.
But you were always apart. You were always two different people. You just didn't notice, until now.

I've also always been surprised at how many same-party relationships disintegrate because of some disagreement over some particular detail of some particular topic, that they generally agree on. To me, it seems like an irrelevant side-topic, but they can't stand to be with this person... and they stomp off. So, I tend to think that it's less that opinions need to align to each other, but rather that opinions need to align in accordance with the level of interpersonal tolerance they can bring into the relationship.
I was raised by relaxed revolutionaries
Maybe I see things this way because my parents come from two diverging political, cultural, national, and ethnic backgrounds, and are prone to disagreeing about a lot of "important" (to people outside their marriage) things, but still have one of the healthiest, most-fruitful, and most long-running marriages of anyone I know, from that generation. My parents, you see, aren't united by their opinions. They're united by their relationship, which is something outside of opinions. Beyond opinions. Relationships are what turn two different people into one, cohesive unit, so that they slowly grow together. Eventually, even their faces merge, and their biological clocks tick to the same rhythm. They eventually become one entity that contains differing opinions about the same topics.
It's like magic, but it's the result of a mindset, not a worldview. Or, as I like to quip:
The best way to stay married, is to not get divorced.

My parents simply determined early on, that they would stay together, and whenever they would find that they disagreed on something that didn't directly pertain to their day-to-day existence with each other they would just agree-to-disagree about that, or roll their eyes, and move on. You do you. Live and let live.
My parents have some of the most strongly held personal opinions of any people I've ever met, but they're also incredibly tolerant and can get along with nearly anyone, so their friends are a confusing hodgepodge of people we liked and found interesting enough to keep around. Which makes their house parties really fun, and highly unusual, in this day and age of mutual-damnation across the aisle.

The things that did affect them, directly, like which school the children should attend or which country they should live in, etc. were things they'd sit down and discuss, and somehow one opinion would emerge, and they'd again... move on.
And that's how my husband and I also live our lives, and it's been working surprisingly well. No topics are off-limits to discussion (so long as you don't drone on for too long), nobody has to give up deeply held beliefs, or stop agitating for the political decisions they prefer.
You see, we didn't like that the other always had the same opinion. We liked that the other always held their opinions strongly. That they were passionate about their opinions. That they were willing to voice their opinions; sacrifice to promote their opinions. And that they didn't let anyone browbeat or cow them, for their opinions, not even their best friends or their spouse. But that they were open to listening to the other side, and trying to wrap their mind around the possibility that they might just be wrong about something.

We married each other because we knew: this person really cares, this person has thought this through, and they're in it, to win it. What "it" is, is mostly irrelevant, so long as it doesn't entail torturing small animals in the basement, or raising the children on a diet of Mountain Dew and porn, or something.
Live and let live. At least, it's never boring. At least, there's always something to ~~argue~~ talk about. At least, we never think... we've just grown apart.
-
 @ eac63075:b4988b48
2024-11-07 21:27:53
@ eac63075:b4988b48
2024-11-07 21:27:53Every night, you draw your curtains without thinking twice. It's instinctive—a simple act that protects your personal space. Yet in our digital lives, we've somehow accepted living in houses made entirely of glass, with countless unseen observers watching our every move.
https://www.fountain.fm/episode/wPZLCJ3fD6vzsWQ3XSE1
Why Privacy Matters to Everyone
Privacy isn't just for those with something to hide; it's a fundamental human need. Think about the conversations you have with friends, the late-night web searches you make, the personal moments you capture in photos. Would you want all of that broadcasted to the world?
I remember my friend Lisa planning a surprise party for her husband. She searched for gift ideas and coordinated with friends through social media. To her dismay, targeted ads for the exact gift she intended to buy started popping up on their shared devices at home. The surprise was ruined. It wasn't malicious, but it was a stark reminder of how our online activities are constantly monitored.
When a major retailer's customer database was breached, my neighbor Sarah discovered her shopping history, credit card details, and even her children's names were exposed to criminals. She hadn't realized how much personal information she'd unknowingly shared through routine purchases. It was a wake-up call that privacy breaches can affect anyone, not just the tech-savvy or those in high-profile positions.
Edward Snowden once said, "Arguing that you don't care about the right to privacy because you have nothing to hide is no different than saying you don't care about free speech because you have nothing to say." Privacy isn't about secrecy; it's about autonomy over our personal information.
The Rise of the Cypherpunks
Back in the '90s, a group known as the cypherpunks saw the writing on the wall. They recognized that as we moved into a digital era, our personal freedoms could be at risk. So they took action.
One of them, Eric Hughes, famously wrote, "Privacy is necessary for an open society in the electronic age." They developed encryption tools to protect individual privacy, laying the groundwork for technologies like Bitcoin and cryptocurrencies. These innovations were about more than digital money; they were about empowering individuals to take control of their own data.
When Technology Knows Too Much
Fast forward to today, and artificial intelligence (AI) is everywhere—in our phones, homes, and even cars. While AI brings convenience, it also raises serious privacy concerns.
Remember when you mentioned needing new running shoes, and suddenly every ad on your browser was for footwear? It's not your imagination. AI algorithms analyze our conversations, searches, and purchases to predict what we'll want next. But where does it stop?
A few years ago, a major retailer guessed a teenager was pregnant based on her shopping habits before she had told her family. They sent her targeted coupons for baby products, leading to a very uncomfortable situation at home. This isn't just marketing—it's intrusion.
Naomi Brockwell, a privacy advocate, warns, "Our relationship with financial privacy has fundamentally changed. What was once seen as a constitutional right and personal freedom is now simply part of the trade-off for using digital payments. Our baseline for what’s acceptable has shifted." It's a wake-up call that our digital footprints are larger and more revealing than we might think.
Privacy-Preserving AI
While AI often threatens privacy, emerging technologies like federated learning offer hope. This approach allows AI models to learn from data without directly accessing personal information. Imagine your phone improving its predictive text without sending your messages to a central server. It's AI that respects your privacy.
The Watchful Eye: Mass Surveillance and AI
Governments and corporations often justify mass surveillance as a means to keep us safe. But at what cost? When every email, message, or phone call can be monitored, we're sacrificing more than just data—we're giving up our freedom to think and communicate without fear.
Think about how you'd behave if someone followed you around with a camera all day. You might avoid certain places or people, censor your conversations, or feel constantly on edge. That's the chilling effect of mass surveillance.
I spoke with Alex, a journalist who covers political activism. "After attending a peaceful protest, I noticed unusual activity on my devices," he told me. "It made me second-guess my work, wondering who's watching." This isn't paranoia; it's a reality for many who challenge the status quo.
Building Digital Fortresses: Cryptographic Innovations
So how do we reclaim our privacy? Cryptography offers some solutions.
Zero-Knowledge Proofs: Proving Without Revealing
Zero-knowledge proofs allow you to prove you know something without revealing the actual information. Imagine showing a bouncer a card that confirms you're over 21 without exposing your birth date or any other details. In the digital world, this means verifying your identity or eligibility without handing over all your personal data.
Homomorphic Encryption: Secure Processing
Then there's homomorphic encryption, which lets companies process your data without actually seeing it. Think of it like sending a locked suitcase with your belongings; they can weigh it or move it, but they can't open it to see what's inside.
Quantum-Resistant Algorithms: Future-Proofing Privacy
As quantum computers become more powerful, they could potentially break current encryption methods. Quantum-resistant algorithms are being developed to safeguard our data against these future threats. It's like reinforcing your digital locks today to withstand the super lock-picking tools of tomorrow.
Decentralization: Taking Back Control
Decentralization aims to put power back into the hands of individuals. Bitcoin let you be your own bank, controlling your finances without a middleman. Decentralized social media platforms like Nostr, Bluesky or Fascaster allow you to own your content without algorithms dictating what you see or who sees you.
Decentralized Identity Systems
Decentralized identity systems let you prove who you are without revealing more than necessary. It's like showing only your age at a bar instead of handing over your entire driver's license. You maintain control over your personal information.
But with great power comes great responsibility. Without a bank to reset your password or customer service to recover your account, the onus is on you to protect your assets and information.
Practical Tips to Protect Your Privacy
You don't have to be a tech guru to safeguard your privacy. Here are some steps you can take today:
-
Use Encrypted Messaging Apps: Switch to apps like Signal, SimpleX or Session for secure communication. Your messages will be end-to-end encrypted, meaning only you and the recipient can read them.
-
Limit Social Media Sharing: Be mindful of what you post. Do you really need to share your location or personal details publicly?
-
Choose Privacy-Focused Browsers and Search Engines: Use browsers like Brave or Firefox and search engines like DuckDuckGo that don't track your every move.
-
Secure Your Passwords: Use strong, unique passwords for each account, and consider a password manager like Bitwarden. Enable two-factor authentication whenever possible.
-
Use Encrypted Email Services: Consider email providers like ProtonMail that offer end-to-end encryption for your communications.
-
Regularly Audit App Permissions: Check which apps have access to your location, microphone, and contacts. Revoke permissions that aren't necessary.
-
Be Wary of Public Wi-Fi: Public networks can be a hotbed for hackers. If you must use them, a VPN like ProtonVPN can add a layer of security.
-
Consider Privacy-Focused Alternatives: Explore services like Nextcloud for cloud storage or Jitsi Meet for video conferencing, which prioritize user privacy.
-
Keep Software Updated: Regular updates often include security patches. Don't ignore them.
-
Stay Informed and Skeptical: Phishing scams are getting more sophisticated. Think before you click on suspicious links or download attachments.
Final Thoughts
Privacy isn't a lost cause; it's a right worth fighting for. As Edward Snowden reminds us, "Privacy is the fountainhead of all other rights."
By taking control of our data and digital habits, we can navigate the online world with greater confidence and peace of mind. After all, wouldn't it be nice to live in a digital home where we decide when to close the curtains?
Read more
OPSEC and Digital Hygiene Plan: https://www.eddieoz.com/opsec-and-digital-hygiene-plan/
-
-
 @ 3bf0c63f:aefa459d
2024-11-07 14:56:17
@ 3bf0c63f:aefa459d
2024-11-07 14:56:17The case against edits
Direct edits are a centralizing force on Nostr, a slippery slope that should not be accepted.
Edits are fine in other, more specialized event kinds, but the
kind:1space shouldn't be compromised with such a push towards centralization, becausekind:1is the public square of Nostr, where all focus should be on decentralization and censorship-resistance.- Why?
Edits introduce too much complexity. If edits are widespread, all clients now have to download dozens of extra events at the same time while users are browsing a big feed of notes which are already coming from dozens of different relays using complicated outbox-model-based querying, then for each event they have to open yet another subscription to these relays -- or perform some other complicated batching of subscriptions which then requires more complexity on the event handling side and then when associating these edits with the original events. I can only imagine this will hurt apps performance, but it definitely raises the barrier to entry and thus necessarily decreases Nostr decentralization.
Some clients may be implemneted in way such that they download tons of events and then store them in a local databases, from which they then construct the feed that users see. Such clients may make edits potentially easier to deal with -- but this is hardly an answer to the point above, since such clients are already more complex to implement in the first place.
- What do you have against complex clients?
The point is not to say that all clients should be simple, but that it should be simple to write a client -- or at least as simple as physically possible.
You may not be thinking about it, but if you believe in the promise of Nostr then we should expect to see Nostr feeds in many other contexts other than on a big super app in a phone -- we should see Nostr notes being referenced from and injected in unrelated webpages, unrelated apps, hardware devices, comment sections and so on. All these micro-clients will have to implement some complicated edit-fetching logic now?
- But aren't we already fetching likes and zaps and other things, why not fetch edits too?
Likes, zaps and other similar things are optional. It's perfectly fine to use Nostr without seeing likes and/or zaps -- and, believe me, it does happen quite a lot. The point is basically that likes or zaps don't affect the content of the main post at all, while edits do.
- But edits are optional!
No, they are not optional. If edits become widespread they necessarily become mandatory. Any client that doesn't implement edits will be displaying false information to its users and their experience will be completely broken.
- That's fine, as people will just move to clients that support edits!
Exactly, that is what I expect to happen too, and this is why I am saying edits are a centralizing force that we should be fighting against, not embracing.
If you understand that edits are a centralizing force, then you must automatically agree that they aren't a desirable feature, given that if you are reading this now, with Nostr being so small, there is a 100% chance you care about decentralization and you're not just some kind of lazy influencer that is only doing this for money.
- All other social networks support editing!
This is not true at all. Bluesky has 10x more users than Nostr and doesn't support edits. Instagram doesn't support editing pictures after they're posted, and doesn't support editing comments. Tiktok doesn't support editing videos or comments after they're posted. YouTube doesn't support editing videos after they're posted. Most famously, email, the most widely used and widespread "social app" out there, does not support edits of any kind. Twitter didn't support edits for the first 15 years of its life, and, although some people complained, it didn't hurt the platform at all -- arguably it benefitted it.
If edits are such a straightforward feature to add that won't hurt performance, that won't introduce complexity, and also that is such an essential feature users could never live without them, then why don't these centralized platforms have edits on everything already? There must be something there.
- Eventually someone will implement edits anyway, so why bother to oppose edits now?
Once Nostr becomes big enough, maybe it will be already shielded from such centralizing forces by its sheer volume of users and quantity of clients, maybe not, we will see. All I'm saying is that we shouldn't just push for bad things now just because of a potential future in which they might come.
- The market will decide what is better.
The market has decided for Facebook, Instagram, Twitter and TikTok. If we were to follow what the market had decided we wouldn't be here, and you wouldn't be reading this post.
- OK, you have convinced me, edits are not good for the protocol. But what do we do about the users who just want to fix their typos?
There are many ways. The annotations spec, for example, provides a simple way to append things to a note without being a full-blown edit, and they fall back gracefully to normal replies in clients that don't implement the full annotations spec.
Eventually we could have annotations that are expressed in form of simple (human-readable?) diffs that can be applied directly to the post, but fall back, again, to comments.
Besides these, a very simple idea that wasn't tried yet on Nostr yet is the idea that has been tried for emails and seems to work very well: delaying a post after the "submit" button is clicked and giving the user the opportunity to cancel and edit it again before it is actually posted.
Ultimately, if edits are so necessary, then maybe we could come up with a way to implement edits that is truly optional and falls back cleanly for clients that don't support them directly and don't hurt the protocol very much. Let's think about it and not rush towards defeat.
-
 @ 4ba8e86d:89d32de4
2024-11-07 13:56:21
@ 4ba8e86d:89d32de4
2024-11-07 13:56:21Tutorial feito por Grom mestre⚡poste original abaixo:
http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/240277/tutorial-criando-e-acessando-sua-conta-de-email-pela-i2p?show=240277#q240277
Bom dia/tarde/noite a todos os camaradas. Seguindo a nossa série de tutoriais referentes a tecnologias essenciais para a segurança e o anonimato dos usuários, sendo as primeiras a openPGP e a I2P, lhes apresento mais uma opção para expandir os seus conhecimentos da DW. Muitos devem conhecer os serviços de mail na onion como DNMX e mail2tor, mas e que tal um serviço de email pela I2P. Nesse tutorial eu vou mostrar a vocês como criar a sua primeira conta no hq.postman.i2p e a acessar essa conta.
É importante que vocês tenham lido a minha primeira série de tutoriais a respeito de como instalar, configurar e navegar pela I2P nostr:nevent1qqsyjcz2w0e6d6dcdeprhuuarw4aqkw730y542dzlwxwssneq3mwpaspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsyp5vcq Esse tutorial é um pré-requisito para o seguinte e portanto recomendo que leia-os antes de prosseguir com o seguinte tutorial. O tutorial de Kleopatra nostr:nevent1qqs8h7vsn5j6qh35949sa60dms4fneussmv9jd76n24lsmtz24k0xlqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgecq8f7 é complementar dado que é extremamente recomendado assinar e criptografar as mensagens que seguem por emails pela DW. Sem mais delongas, vamos ao tutorial de fato.
1. Criando uma conta de email no hq.postman
Relembrando: Esse tutorial considera que você já tenha acesso à I2P. Entre no seu navegador e acesse o endereço hq.postman.i2p. O roteador provavelmente já contém esse endereço no seu addressbook e não haverá a necessidade de inserir o endereço b32 completo. Após entrar no site vá para a página '1 - Creating a mailbox' https://image.nostr.build/d850379fe315d2abab71430949b06d3fa49366d91df4c9b00a4a8367d53fcca3.jpg
Nessa página, insira as credenciais de sua preferências nos campos do formulário abaixo. Lembre-se que o seu endereço de email aceita apenas letras e números. Clique em 'Proceed' depois que preencher todos os campos. https://image.nostr.build/670dfda7264db393e48391f217e60a2eb87d85c2729360c8ef6fe0cf52508ab4.jpg
Uma página vai aparecer pedindo para confirmar as credenciais da sua nova conta. Se tudo estiver certo apenas clique em 'Confirm and Create Mailbox'. Se tudo ocorrer como conforme haverá uma confirmação de que a sua nova conta foi criada com sucesso. Após isso aguarde por volta de 5 minutos antes de tentar acessá-la, para que haja tempo suficiente para o servidor atualizar o banco de dados. https://image.nostr.build/ec58fb826bffa60791fedfd9c89a25d592ac3d11645b270c936c60a7c59c067f.jpg https://image.nostr.build/a2b7710d1e3cbb36431acb9055fd62937986b4da4b1a1bbb06d3f3cb1f544fd3.jpg
Pronto! Sua nova conta de email na I2P foi criada. Agora vamos para a próxima etapa: como acessar a sua conta via um cliente de email.
2. Configurando os túneis cliente de SMTP e POP3
O hq.postman não possui um cliente web que nos permite acessar a nossa conta pelo navegador. Para isso precisamos usar um cliente como Thunderbird e configurar os túneis cliente no I2Pd que serão necessários para o Thunderbird se comunicar com o servidor pela I2P.
Caso não tenha instalado o Thunderbird ainda, faça-o agora antes de prosseguir.
Vamos configurar os túneis cliente do servidor de email no nosso roteador. Para isso abra um terminal ou o seu gestor de arquivos e vá para a pasta de configuração de túneis do I2P. Em Linux esse diretório se localiza em /etc/i2pd/tunnels.d. Em Windows, essa pasta se localiza em C:\users\user\APPDATA\i2pd. Na pasta tunnels.d crie dois arquivos: smtp.postman.conf e pop-postman.conf. Lembre-se que em Linux você precisa de permissões de root para escrever na pasta de configuração. Use o comando sudoedit
para isso. Edite-os conforme as imagens a seguir:
Arquivo pop-postman.conf https://image.nostr.build/7e03505c8bc3b632ca5db1f8eaefc6cecb4743cd2096d211dd90bbdc16fe2593.jpg
Arquivo smtp-postman.conf https://image.nostr.build/2d06c021841dedd6000c9fc2a641ed519b3be3c6125000b188842cd0a5af3d16.jpg
Salve os arquivos e reinicie o serviço do I2Pd. Em Linux isso é feito pelo comando:
sudo systemctl restart i2pdEntre no Webconsole do I2Pd pelo navegador (localhost:7070) e na seção I2P Tunnels, verifique se os túneis pop-postman e smtp-postman foram criados, caso contrário verifique se há algum erro nos arquivos e reinicie o serviço.Com os túneis cliente criados, vamos agora configurar o Thunderbird
3. Configurando o Thunderbird para acessar a nossa conta
Abra o Thunderbird e clique em criar uma nova conta de email. Se você não tiver nenhum conta previamente presente nele você vai ser diretamente recebido pela janela de criação de conta a seguir. https://image.nostr.build/e9509d7bd30623716ef9adcad76c1d465f5bc3d5840e0c35fe4faa85740f41b4.jpg https://image.nostr.build/688b59b8352a17389902ec1e99d7484e310d7d287491b34f562b8cdd9dbe8a99.jpg
Coloque as suas credenciais, mas não clique ainda em Continuar. Clique antes em Configure Manually, já que precisamos configurar manualmente os servidores de SMTP e POP3 para, respectivamente, enviar e receber mensagens.
Preencha os campos como na imagem a seguir. Detalhe: Não coloque o seu endereço completo com o @mail.i2p, apenas o nome da sua conta. https://image.nostr.build/4610b0315c0a3b741965d3d7c1e4aff6425a167297e323ba8490f4325f40cdcc.jpg
Clique em Re-test para verificar a integridade da conexão. Se tudo estiver certo uma mensagem irá aparecer avisando que as configurações do servidores estão corretas. Clique em Done assim que estiver pronto para prosseguir. https://image.nostr.build/8a47bb292f94b0d9d474d4d4a134f8d73afb84ecf1d4c0a7eb6366d46bf3973a.jpg
A seguinte mensagem vai aparecer alertando que não estamos usando criptografia no envio das credenciais. Não há problema nenhum aqui, pois a I2P está garantindo toda a proteção e anonimato dos nossos dados, o que dispensa a necessidade de uso de TLS ou qualquer tecnologia similar nas camadas acima. Marque a opção 'I Understand the risks' e clique em 'Continue' https://image.nostr.build/9c1bf585248773297d2cb1d9705c1be3bd815e2be85d4342227f1db2f13a9cc6.jpg
E por fim, se tudo ocorreu como devido sua conta será criada com sucesso e você agora será capaz de enviar e receber emails pela I2P usando essa conta. https://image.nostr.build/8ba7f2c160453c9bfa172fa9a30b642a7ee9ae3eeb9b78b4dc24ce25aa2c7ecc.jpg
4. Observações e considerações finais
Como informado pelo próprio site do hq.postman, o domínio @mail.i2p serve apenas para emails enviados dentro da I2P. Emails enviados pela surface devem usar o domínio @i2pmai.org. É imprescindível que você saiba usar o PGP para assinar e criptografar as suas mensagens, dado que provavelmente as mensagens não são armazenadas de forma criptografada enquanto elas estão armazenadas no servidor. Como o protocolo POP3 delete as mensagens no imediato momento em que você as recebe, não há necessidade de fazer qualquer limpeza na sua conta de forma manual.
Por fim, espero que esse tutorial tenha sido útil para vocês. Que seu conhecimento tenha expandido ainda mais com as informações trazidas aqui. Até a próxima.
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-09 15:00:44
@ 5d4b6c8d:8a1c1ee3
2024-11-09 15:00:44The wife and I were drinking our coffee, while a fair bit of commotion was coming from our daughter in the bathroom.
She came out and very shyly said "'Scuse me."
We've been working with her on manners and not interrupting, so this was very encouraging.
She continued very sweetly, "There's a pwoblem in the potty."
That was decidedly less encouraging.
originally posted at https://stacker.news/items/760318
-
 @ 72592ec9:ffa64d2c
2024-11-09 11:00:37
@ 72592ec9:ffa64d2c
2024-11-09 11:00:37Really good read so far, thought I'd share this part from https://bitcoindevphilosophy.com/
It seems that we can’t have a decentralized system based on trust, and that’s why trustlessness is important in Bitcoin.
To use Bitcoin in a trustless manner, you have to run a fully-validating Bitcoin node. Only then will you be able to verify that the blocks you receive from others are following the consensus rules; for example, that the coin issuance schedule is kept and that no double-spends occur on the blockchain. If you don’t run a full node, you outsource verification of Bitcoin blocks to someone else and trust them to tell you the truth, which means you’re not using Bitcoin trustlessly.
Diagram David Harding has authored an article on the bitcoin.org website explaining how running a full node - or using Bitcoin trustlessly - actually helps you.
The bitcoin currency only works when people accept bitcoins in exchange for other valuable things. That means it’s the people accepting bitcoins who give it value and who get to decide how Bitcoin should work.
When you accept bitcoins, you have the power to enforce Bitcoin’s rules, such as preventing confiscation of any person’s bitcoins without access to that person’s private keys.
Unfortunately, many users outsource their enforcement power. This leaves Bitcoin’s decentralization in a weakened state where a handful of miners can collude with a handful of banks and free services to change Bitcoin’s rules for all those non-verifying users who outsourced their power.
Unlike other wallets, Bitcoin Core does enforce the rules—so if the miners and banks change the rules for their non-verifying users, those users will be unable to pay full validation Bitcoin Core users like you.
— David Harding Full Validation on bitcoin.org (2015) He says that running a full node will help you verify every aspect of the blockchain without trusting anyone else, so as to ensure that the coins you receive from others are genuine. This is great, but there’s one important thing that a full node can’t help you with: it can’t prevent double- spending through chain rewrites:
Note that although all programs—including Bitcoin Core—are vulnerable to chain rewrites, Bitcoin provides a defense mechanism: the more confirmations your transactions have, the safer you are. There is no known decentralized defense better than that.
— David Harding Full Validation on bitcoin.org (2015) No matter how advanced your software is, you still have to trust that the blocks containing your coins won’t be rewritten. However, as pointed out by Harding, you can await a number of confirmations, after which you consider the probability of a chain rewrite small enough to be acceptable.
The incentives for using Bitcoin in a trustless way align with the system’s need for full node decentralization. The more people who use their own full nodes, the more full node decentralization, and thus the stronger Bitcoin stands against malicious changes to the protocol. But unfortunately, as explained in the full node decentralization section, users often opt for trusted services as consequence of the inevitable trade-off between trustlessness and convenience.
originally posted at https://stacker.news/items/760051
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-09 04:02:26
@ 5d4b6c8d:8a1c1ee3
2024-11-09 04:02:26As always, we're going to lead off with the on-going contests at ~Stacker_Sports.
@BlokchainB requested some NHL coverage, so @grayruby is going to try to explain hockey to me.
We'll check in on the NFL post trade deadline and see if the landscape shifted appreciably. Also, we had a requested topic on why the top picks of the past two drafts are paling in comparison to the guys taken immediately after them. Tune is as we flounder for answers.
We had some disagreements on our hastily slapped together NBA power rankings, so we'll have to hash those out. Thankfully, @BlokchainB has already confirmed that mine were better.
Then I wanted to talk about Predyx in a little more detail, because they're on Stacker News and their project is very cool. I'm sure we'll cover our other gambling (mis)adventures.
What say you about any of those topics? Are there other topics you want our thoughts on?
The Stacker Sports Pod is for stackers by stackers.
originally posted at https://stacker.news/items/759836
-
 @ 8d34bd24:414be32b
2024-11-03 15:17:36
@ 8d34bd24:414be32b
2024-11-03 15:17:36I was recently having a friendly discussion about end-times eschatology. I believe the Bible communicates a pre-tribulation rapture of believers before an actual 7 year tribulation followed by a literal thousand year reign of Jesus on Earth before Armageddon and the Great White Throne Judgement. My friend said he thought the rapture had happened around 70 AD. I had never heard anyone make that argument, so I asked for scriptural evidence. He gave me these three verses:
“Truly I say to you, there are some of those who are standing here who will not taste death until they see the Son of Man coming in His kingdom.” (Matthew 16:28)
And Jesus was saying to them, “Truly I say to you, there are some of those who are standing here who will not taste death until they see the kingdom of God after it has come with power.” (Mark 9:1)
But I say to you truthfully, there are some of those standing here who will not taste death until they see the kingdom of God.” (Luke 9:27)
These three verses do sound like some of those standing before Jesus will be raptured, although the words are “see the kingdom of God.”
I always seek to know what I believe and why I believe it and to make sure that I am not misled about anything regarding the Bible, so I stopped and thought and listened. I know that most of the Bible strongly suggests that the rapture happens immediately before the tribulation, but these verses seem to contradict that conclusion. God gave me the following passage of a discussion between Peter and Jesus right after Jesus told Peter how he would die:
Peter, turning around, saw the disciple whom Jesus loved following them; the one who also had leaned back on His bosom at the supper and said, “Lord, who is the one who betrays You?” So Peter seeing him said to Jesus, “Lord, and what about this man?” Jesus said to him, “If I want him to remain until I come, what is that to you? You follow Me!” Therefore this saying went out among the brethren that that disciple would not die; yet Jesus did not say to him that he would not die, but only, “If I want him to remain until I come, what is that to you?” (John 21:20-23) {emphasis mine}
Jesus’s statements made His disciples think that the Apostle John would live until Jesus returned, but that wasn’t what Jesus was communicating. I think this misunderstanding is similar to the one in the three verses above. John did live longer than any of His other disciples. Near the end of John’s life, after all of the other disciples had passed away, Jesus brought him to heaven in the spirit:
I, John, your brother and fellow partaker in the tribulation and kingdom and perseverance which are in Jesus, was on the island called Patmos because of the word of God and the testimony of Jesus. I was in the Spirit on the Lord’s day, and I heard behind me a loud voice like the sound of a trumpet, saying, “Write in a book what you see, and send it to the seven churches: to Ephesus and to Smyrna and to Pergamum and to Thyatira and to Sardis and to Philadelphia and to Laodicea.”
Then I turned to see the voice that was speaking with me. And having turned I saw seven golden lampstands; and in the middle of the lampstands I saw one like a son of man, clothed in a robe reaching to the feet, and girded across His chest with a golden sash. His head and His hair were white like white wool, like snow; and His eyes were like a flame of fire. His feet were like burnished bronze, when it has been made to glow in a furnace, and His voice was like the sound of many waters. In His right hand He held seven stars, and out of His mouth came a sharp two-edged sword; and His face was like the sun shining in its strength. (Revelation 1:9-16) {emphasis mine}
In this vision, before John’s death, he saw “the kingdom of God” in heaven. This alone would fulfill Jesus’s statement, but there is more.
Then slightly later in Revelation:
After these things I looked, and behold, a door standing open in heaven, and the first voice which I had heard, like the sound of a trumpet speaking with me, said, “Come up here, and I will show you what must take place after these things.” Immediately I was in the Spirit; and behold, a throne was standing in heaven, and One sitting on the throne. (Revelation 4:1-2)
In this passage, John is called up to heaven to see “what must take place after these things.” What does John see about what is to come? He “see[s] the Son of Man coming in His kingdom.”(Matthew 16:28b)
John was listening to Jesus’s promise that “there are some of those standing here who will not taste death until they see the kingdom of God.” (Mark 9:1) In his old age, he was temporarily called to heaven to see the “the kingdom of God” and “the Son of Man coming in His kingdom.” John did see the things that Jesus promised before he “tasted death.” It wasn’t that Jesus came back or raptured the church before John died. It was that Jesus brought John into heaven in the spirit to see what would later come to be. Jesus then returned John back to earth to live out what remained of his life.
When I asked my husband to review my post, he made another explanation of the original three verses. I’ll use Matthew for this explanation.
28 “Truly I say to you, there are some of those who are standing here who will not taste death until they see the Son of Man coming in His kingdom.” (Matthew 16:28)
The very next verses are these:
Six days later Jesus took with Him Peter and James and John his brother, and led them up on a high mountain by themselves. And He was transfigured before them; and His face shone like the sun, and His garments became as white as light. And behold, Moses and Elijah appeared to them, talking with Him. Peter said to Jesus, “Lord, it is good for us to be here; if You wish, I will make three tabernacles here, one for You, and one for Moses, and one for Elijah.” While he was still speaking, a bright cloud overshadowed them, and behold, a voice out of the cloud said, “This is My beloved Son, with whom I am well-pleased; listen to Him!” (Matthew 17:1-5)
The transfiguration was the initiation of Jesus reign and Peter, James, and John were able to see Jesus in His glorified form. Since this happened 6 days later, it stands out as a fulfillment. You could argue that both my idea and my husband’s are a fulfillment of Jesus’s promise.
It also does not make sense that the church was raptured in Jesus’s generation because Jesus’s kingdom did not come at that time. The evil in the world from His ascension to today is clearly not His kingdom. Also, nowhere in Revelation is the church mentioned (although people do come to know Jesus). This is because God took His church home to be with Him.
For God has not destined us for wrath, but for obtaining salvation through our Lord Jesus Christ, (1 Thessalonians 5:9)
The seven year tribulation is the wrath of God poured out on those who rejected their Creator and Savior. “God has not destined us for wrath.”
There will be a wonderful, literal thousand year reign of Jesus. Satan and his demons will be bound and will no longer being leading people away from Jesus. It will be a time of peace for 1000 years. Sadly a large number of people who live during the millennium will not put their faith in Jesus, but will rebel against Him when Satan is released one last time. Their rebellion will lead to their physical death and eternal torment.
Reading all of these verses, I once again see that even when there seems to be a contradiction, there is none. I still believe the rapture is yet to come and will occur shortly before the seven year tribulation. I still believe that the rapture and the tribulation are coming soon. I’m also glad that I took the time to look at the evidence, consider it logically, and consider the Bible in its entirety instead of blindly digging in my heels and claiming fiat, “I am right.”
I guess I should also share the two most explicit passages in the Bible on the rapture, so you can fully understand what is being talked about in this article:
But we do not want you to be uninformed, brethren, about those who are asleep, so that you will not grieve as do the rest who have no hope. For if we believe that Jesus died and rose again, even so God will bring with Him those who have fallen asleep in Jesus. For this we say to you by the word of the Lord, that we who are alive and remain until the coming of the Lord, will not precede those who have fallen asleep. For the Lord Himself will descend from heaven with a shout, with the voice of the archangel and with the trumpet of God, and the dead in Christ will rise first. Then we who are alive and remain will be caught up together with them in the clouds to meet the Lord in the air, and so we shall always be with the Lord. Therefore comfort one another with these words. (1 Thessalonians 4:13-18) {emphasis mine}
This verse means even more when we look back at Jesus’s ascension:
And after He had said these things, He was lifted up while they were looking on, and a cloud received Him out of their sight. And as they were gazing intently into the sky while He was going, behold, two men in white clothing stood beside them. They also said, “Men of Galilee, why do you stand looking into the sky? This Jesus, who has been taken up from you into heaven, will come in just the same way as you have watched Him go into heaven.” (Acts 1:9-11) {emphasis mine}
The other most explicit passage on the rapture is this:
Behold, I tell you a mystery; we will not all sleep, but we will all be changed, in a moment, in the twinkling of an eye, at the last trumpet; for the trumpet will sound, and the dead will be raised imperishable, and we will be changed. For this perishable must put on the imperishable, and this mortal must put on immortality. But when this perishable will have put on the imperishable, and this mortal will have put on immortality, then will come about the saying that is written, “Death is swallowed up in victory. (1 Corinthians 15:51-54) {emphasis mine}
In the New Testament, the Bible always calls the death of believers “sleep,” because it is not an end. It is a new beginning. I hope you are looking forward to the day when believers “will all be changed, in a moment, in the twinkling of an eye, at the last trumpet.”
God is good! All of the time! I hope to meet you all when we are called up to meet Jesus in the air.
Trust Jesus.\ \ your sister in Christ,
Christy
NOTE: I know this article is a bit different because it documents my whole thought process rather than just speaking clearly what I believe God’s word says. I hope it has been a blessing to you and I’d love feedback.
NOTE: Also, my last long form article, I never was able to see posted. Would someone please comment or like so I can make sure these are posting. This editor is easiest for me because I don't have to redo the editing, but if the posts aren't getting to people, I'll need to post using another editor. Thanks for your help.
-
 @ bcea2b98:7ccef3c9
2024-11-09 01:30:29
@ bcea2b98:7ccef3c9
2024-11-09 01:30:29@chess h3
originally posted at https://stacker.news/items/759635
-
 @ eac63075:b4988b48
2024-10-30 20:58:01
@ eac63075:b4988b48
2024-10-30 20:58:01Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions.
https://www.fountain.fm/episode/hVVS7hrsX8VQ9SPoUYbg
What Are Cryptocurrencies?
Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably.
The Origin of the Myth: Cryptocurrencies and Illicit Activities
The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use.
Current Data: Cryptocurrencies and Illicit Activities
According to the 2024 Cryptocurrency Crime Report from Chainalysis, only 0.34% of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities.
 ## Comparison with Traditional Money
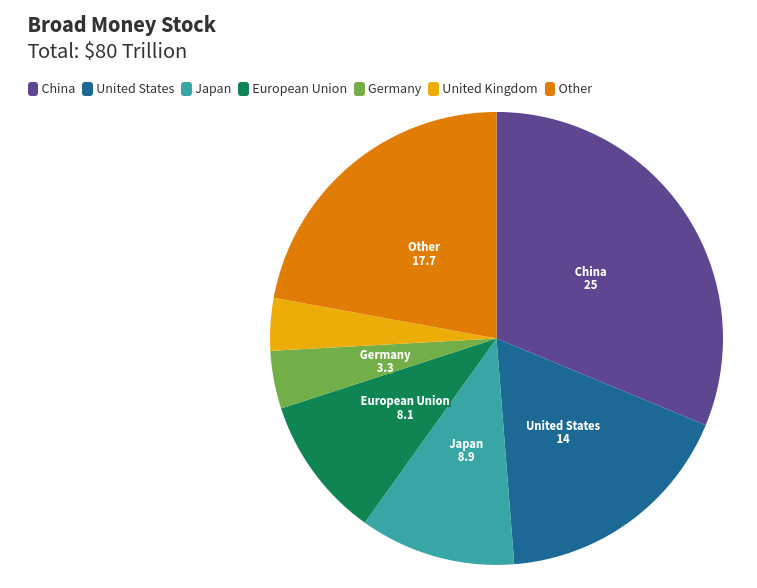
## Comparison with Traditional MoneyWhen we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. According to a report by Verafin, about 3.1 trillion dollars are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately 3.87% of all money in circulation.
 In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies.
In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies.The Transparency of Blockchain
One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record.
Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace.
How Much Money Is There in the World?
To understand the scale, it’s interesting to know that, according to the World Population Review, about 80 trillion dollars are in circulation globally, including physical and digital money. Out of this total, only 5 trillion dollars is in physical cash. This shows that most transactions are already digital, even in the traditional financial system.
 ## Cryptocurrencies Promote Economic Freedom
## Cryptocurrencies Promote Economic FreedomCryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services.
This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them.
Myths and Realities
It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation.
Conclusion: Are Cryptocurrencies Really the Villains?
The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception.
If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause.
And You, What Do You Think?
Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion!Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions.
What Are Cryptocurrencies? Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably.
The Origin of the Myth: Cryptocurrencies and Illicit Activities The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use.
Current Data: Cryptocurrencies and Illicit Activities According to the 2024 Cryptocurrency Crime Report from Chainalysis, only 0.34% of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities.
Comparison with Traditional Money When we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. According to a report by Verafin, about 3.1 trillion dollars are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately 3.87% of all money in circulation.
In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies.
The Transparency of Blockchain One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record.
Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace.
How Much Money Is There in the World? To understand the scale, it’s interesting to know that, according to the World Population Review, about 80 trillion dollars are in circulation globally, including physical and digital money. Out of this total, only 5 trillion dollars is in physical cash. This shows that most transactions are already digital, even in the traditional financial system.
Cryptocurrencies Promote Economic Freedom Cryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services.
This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them.
Myths and Realities It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation.
Conclusion: Are Cryptocurrencies Really the Villains? The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception.
If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause.
And You, What Do You Think? Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion!
-
 @ b4403b24:83542d4e
2024-11-08 22:34:45
@ b4403b24:83542d4e
2024-11-08 22:34:45Imagine what will be in the upcoming years if this trend continues.
Bullish 🚀🌕
originally posted at https://stacker.news/items/759487
-
 @ 3f770d65:7a745b24
2024-10-29 17:38:20
@ 3f770d65:7a745b24
2024-10-29 17:38:20Amber
Amber is a Nostr event signer for Android that allows users to securely segregate their private key (nsec) within a single, dedicated application. Designed to function as a NIP-46 signing device, Amber ensures your smartphone can sign events without needing external servers or additional hardware, keeping your private key exposure to an absolute minimum. This approach aligns with the security rationale of NIP-46, which states that each additional system handling private keys increases potential vulnerability. With Amber, no longer do users need to enter their private key into various Nostr applications.

Amber is supported by a growing list of apps, including Amethyst, 0xChat, Voyage, Fountain, and Pokey, as well as any web application that supports NIP-46 NSEC bunkers, such as Nostr Nests, Coracle, Nostrudel, and more. With expanding support, Amber provides an easy solution for secure Nostr key management across numerous platforms.

Amber supports both native and web-based Nostr applications, aiming to eliminate the need for browser extensions or web servers. Key features include offline signing, multiple account support, and NIP-46 compatibility, and includes a simple UI for granular permissions management. Amber is designed to support signing events in the background, enhancing flexibility when you select the "remember my choice" option, eliminating the need to constantly be signing events for applications that you trust. You can download the app from it's GitHub page, via Obtainium or Zap.store.
To log in with Amber, simply tap the "Login with Amber" button or icon in a supported application, or you can paste the NSEC bunker connection string directly into the login box. For example, use a connection string like this: bunker://npub1tj2dmc4udvgafxxxxxxxrtgne8j8l6rgrnaykzc8sys9mzfcz@relay.nsecbunker.com.

Citrine
Citrine is a Nostr relay built specifically for Android, allowing Nostr clients on Android devices to seamlessly send and receive events through a relay running directly on their smartphone. This mobile relay setup offers Nostr users enhanced flexibility, enabling them to manage, share, and back up all their Nostr data locally on their device. Citrine’s design supports independence and data security by keeping data accessible and under user control.

With features tailored to give users greater command over their data, Citrine allows easy export and import of the database, restoration of contact lists in case of client malfunctions, and detailed relay management options like port configuration, custom icons, user management, and on-demand relay start/stop. Users can even activate TOR access, letting others connect securely to their Nostr relay directly on their phone. Future updates will include automatic broadcasting when the device reconnects to the internet, along with content resolver support to expand its functionality.
Once you have your Citrine relay fully configured, simply add it to the Private and Local relay sections in Amethyst's relay configuration.

Pokey
Pokey for Android is a brand new, real-time notification tool for Nostr. Pokey allows users to receive live updates for their Nostr events and enabling other apps to access and interact with them. Designed for seamless integration within a user's Nostr relays, Pokey lets users stay informed of activity as it happens, with speed and the flexibility to manage which events trigger notifications on their mobile device.

Pokey currently supports connections with Amber, offering granular notification settings so users can tailor alerts to their preferences. Planned features include broadcasting events to other apps, authenticating to relays, built-in Tor support, multi-account handling, and InBox relay management. These upcoming additions aim to make Pokey a fantastic tool for Nostr notifications across the ecosystem.
Zap.store
Zap.store is a permissionless app store powered by Nostr and your trusted social graph. Built to offer a decentralized approach to app recommendations, zap.store enables you to check if friends like Alice follow, endorse, or verify an app’s SHA256 hash. This trust-based, social proof model brings app discovery closer to real-world recommendations from friends and family, bypassing centralized app curation. Unlike conventional app stores and other third party app store solutions like Obtainium, zap.store empowers users to see which apps their contacts actively interact with, providing a higher level of confidence and transparency.

Currently available on Android, zap.store aims to expand to desktop, PWAs, and other platforms soon. You can get started by installing Zap.store on your favorite Android device, and install all of the applications mentioned above.
Android's openness goes hand in hand with Nostr's openness. Enjoy exploring both expanding ecosystems.
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-08 13:59:13
@ 5d4b6c8d:8a1c1ee3
2024-11-08 13:59:13@Coffee proposed a topic for The Stacker Sports Podcast on our nostr thread and I wanted to share it here.
Why have the top picks in the past two drafts (Bryce Young and Caleb Williams) been so significantly outplayed by the players taken immediately after them (CJ Stroud and Jayden Daniels)?
It's early in the careers of each of these players, but Stroud and Daniels are already looking like MVP caliber franchise QB's. Why did teams miss this?
The most obvious hypothesis (that the Bears and Panthers flubbed their picks) doesn't make much sense, because Young and Williams were the consensus top picks in their drafts.
A bigger question is why it's so difficult to spot an MVP caliber QB from their college play.
originally posted at https://stacker.news/items/758917
-
 @ c11cf5f8:4928464d
2024-11-08 13:31:22
@ c11cf5f8:4928464d
2024-11-08 13:31:22The Magnificent 7:
Here we are again with our monthly Magnificent Seven summary, trying to give you a hit of what you missed this month in the ~AGORA territory.
Top-Performing Ads
This month, the most zapranked ones are:
01[OFFER] IPv4+IPv6 KVM VPS, from 1.75EUR/month (Stockholm/SE SWEDEN) by @skhron02[SWAP] SN Cowboy credits by @DarthCoin03[SELL] “NO⚡️TR T-Shirt” for 21K sats by @thebullishbitcoiner04[sell] iptv subscription 10k+ live tv channels and 20k+ vod (tv/movies) by @profullstack
This month we ran short, so here other 3 from previous month *
05[SELL] StackerNews Archived Territories - Your chance to own a piece of history! by @Design_r *06[SELL] Stickers for Stackers! SN Nostr Badges vinyl stickers - from 3,456 sats by @AGORA *07[SELL] 3 WishMesh Meshtastic radios and 2 extended antennas 325,000 SATS by @fe3c522a6f
In case you missed
Here some interesting post opening conversation and free speech:
@supratic share some interesting tools for merchants and businesses: - https://stacker.news/items/745053/r/AG TinyPine: A simple LN and CASHU ecash POS system for merchants - https://stacker.news/items/750705/r/AG PLEBEIAN – Simple, Anonymous & Free Market for Everyone
And here some more insights on how to do business in the private: - https://stacker.news/items/732291/r/AG Classifieds vs. Listings: Navigating Nostr Protocol's Approach to Advertising by @AGORA - https://stacker.news/items/742973/r/AG The Watchman Privacy Podcast – Escape the Servile Society with Vonu by @mo - https://stacker.news/items/746325/r/AG How to Operate a Business in the Private with Trust by @mo - https://stacker.news/items/741906/r/AG Paying out debt and bills using the Bills of Exchange act by @supratic - https://stacker.news/items/751074/r/AG The Separation of Business and State by @mo - https://stacker.news/items/718979/r/AG Mystery Paper: Ancient Merchant Paper, For Merchants Only & Corporate Countries by @AGORA - https://stacker.news/items/720288/r/AG Parallel Society • Free Man's Perspective by @DarthCoin
🏷️ Spending Sunday is back!
Share your most recent Bitcoin purchases of just check what other stackers are buying with their sats! Read more https://stacker.news/items/721244/r/AG
Just a reminder for you all
This territory aims to connect stackers and curious buyers for IRL P2P Bitcoin deals. Have fun checking what else stackers are shilling globally in the ~AGORA. This is a great time for you to make some space un-dusting some stuff that has been sitting there for too long and get some sats for it!
To incentivize more conversation and a more libre mindset, we decided to adopt the zapshare approach, so we'll split the rewards of this TM7 to the best contributors plus zaps to the posts that offer much PoW when posting.
Create your Ads now!
Looking to start something new? Hit one of the links below to free your mind:
- 💬 TOPIC for conversation,
- [⚖️ SELL] anything! or,
- if you're looking for something, hit the [🛒 BUY]!
- [🧑💻 HIRE] any bitcoiner skill or stuff from bitcoiners
- [🖇 OFFER] any product or service and stack more sats
- [🧑⚖️ AUCTION] to let stackers decide a fair price for your item
- [🤝 SWAP] if you're looking to exchange anything with anything else
- [🆓 FREE] your space, make a gift!
- [⭐ REVIEW] any bitcoin product or LN service you recently bought or subscribed to
Or contact @AGORA team on nostr DM and we can help you publish a personalized post.
Coinomi Bitcoin Testnet skull quantum digital allow faculty enforce spatial emotion fun candy plunge stick stairs salad dish pass fix between shock scene ivory cargo unhappy fault
originally posted at https://stacker.news/items/758878
-
 @ 3f770d65:7a745b24
2024-10-29 17:34:34
@ 3f770d65:7a745b24
2024-10-29 17:34:34Amber
Amber is a Nostr event signer for Android that allows users to securely segregate their private key (nsec) within a single, dedicated application. Designed to function as a NIP-46 signing device, Amber ensures your smartphone can sign events without needing external servers or additional hardware, keeping your private key exposure to an absolute minimum. This approach aligns with the security rationale of NIP-46, which states that each additional system handling private keys increases potential vulnerability. With Amber, no longer do users need to enter their private key into various Nostr applications.

Amber is supported by a growing list of apps, including Amethyst, 0xChat, Voyage, Fountain, and Pokey, as well as any web application that supports NIP-46 NSEC bunkers, such as Nostr Nests, Coracle, Nostrudel, and more. With expanding support, Amber provides an easy solution for secure Nostr key management across numerous platforms.

Amber supports both native and web-based Nostr applications, aiming to eliminate the need for browser extensions or web servers. Key features include offline signing, multiple account support, and NIP-46 compatibility, and includes a simple UI for granular permissions management. Amber is designed to support signing events in the background, enhancing flexibility when you select the "remember my choice" option, eliminating the need to constantly be signing events for applications that you trust. You can download the app from it's GitHub page, via Obtainium or Zap.store.
To log in with Amber, simply tap the "Login with Amber" button or icon in a supported application, or you can paste the NSEC bunker connection string directly into the login box. For example, use a connection string like this: bunker://npub1tj2dmc4udvgafxxxxxxxrtgne8j8l6rgrnaykzc8sys9mzfcz@relay.nsecbunker.com.

Citrine
Citrine is a Nostr relay built specifically for Android, allowing Nostr clients on Android devices to seamlessly send and receive events through a relay running directly on their smartphone. This mobile relay setup offers Nostr users enhanced flexibility, enabling them to manage, share, and back up all their Nostr data locally on their device. Citrine’s design supports independence and data security by keeping data accessible and under user control.

With features tailored to give users greater command over their data, Citrine allows easy export and import of the database, restoration of contact lists in case of client malfunctions, and detailed relay management options like port configuration, custom icons, user management, and on-demand relay start/stop. Users can even activate TOR access, letting others connect securely to their Nostr relay directly on their phone. Future updates will include automatic broadcasting when the device reconnects to the internet, along with content resolver support to expand its functionality.
Once you have your Citrine relay fully configured, simply add it to the Private and Local relay sections in Amethyst's relay configuration.

Pokey
Pokey for Android is a brand new, real-time notification tool for Nostr. Pokey allows users to receive live updates for their Nostr events and enabling other apps to access and interact with them. Designed for seamless integration within a user's Nostr relays, Pokey lets users stay informed of activity as it happens, with speed and the flexibility to manage which events trigger notifications on their mobile device.

Pokey currently supports connections with Amber, offering granular notification settings so users can tailor alerts to their preferences. Planned features include broadcasting events to other apps, authenticating to relays, built-in Tor support, multi-account handling, and InBox relay management. These upcoming additions aim to make Pokey a fantastic tool for Nostr notifications across the ecosystem.
Zap.store
Zap.store is a permissionless app store powered by Nostr and your trusted social graph. Built to offer a decentralized approach to app recommendations, zap.store enables you to check if friends like Alice follow, endorse, or verify an app’s SHA256 hash. This trust-based, social proof model brings app discovery closer to real-world recommendations from friends and family, bypassing centralized app curation. Unlike conventional app stores and other third party app store solutions like Obtainium, zap.store empowers users to see which apps their contacts actively interact with, providing a higher level of confidence and transparency.

Currently available on Android, zap.store aims to expand to desktop, PWAs, and other platforms soon. You can get started by installing Zap.store on your favorite Android device, and install all of the applications mentioned above.
Android's openness goes hand in hand with Nostr's openness. Enjoy exploring both expanding ecosystems.
-
 @ 3ffac3a6:2d656657
2024-10-28 16:11:58
@ 3ffac3a6:2d656657
2024-10-28 16:11:58Manifesto Stancap (Stalinismo Anarco-Capitalista):
Por um Futuro de Controle Absoluto e Liberdade Ilimitada
Saudações, camaradas e consumidores! Hoje, convocamos todos a marchar com orgulho rumo à mais avançada utopia jamais concebida pelo pensamento humano (e nem tão humano assim): o Stancap, a síntese perfeita entre a mão invisível do mercado e o punho de ferro do Estado.
1. Liberdade Total sob o Controle Absoluto
Aqui, a liberdade é garantida. Você é livre para fazer o que quiser, pensar o que quiser, mas lembre-se: nós estaremos observando — por uma taxa de assinatura mensal, é claro. O governo será privatizado e administrado por CEOs visionários que entendem que os lucros mais seguros vêm da ordem e do controle. Sim, camarada, a ordem é o que nos liberta!
2. Empresas Estatais e Governo Privado para o Progresso Econômico
Todas as empresas serão estatizadas. Afinal, queremos um mercado forte e estável, e nada diz "eficiência" como uma gestão estatal unificada sob nosso Grande Conselho Corporativo. E para garantir o controle absoluto e a segurança dos cidadãos, o governo também será privatizado, operando sob princípios empresariais e contratos de eficiência. Nosso governo privado, liderado por CEOs que representam o mais alto nível de comprometimento e lucros, estará alinhado com o progresso e a ordem. Suas preferências de consumo serão registradas, analisadas e programadas para otimizar sua experiência como cidadão-produto. Cada compra será um voto de confiança, e qualquer recusa será gentilmente "corrigida".
3. Liberdade de Expressão Absoluta (com Moderação, Claro)
A liberdade de expressão é sagrada. Fale o que quiser, onde quiser, para quem quiser! Mas cuidado com o que você diz. Para garantir a pureza de nossas ideias e manter a paz, qualquer expressão que se desvie de nosso ideal será gentilmente convidada a uma estadia em um de nossos premiados Gulags Privados™. Neles, você terá a oportunidade de refletir profundamente sobre suas escolhas, com todo o conforto que um regime totalitário pode proporcionar.
4. A Ditadura da Liberdade
Dizemos sem ironia: a única verdadeira liberdade é aquela garantida pela ditadura. Com nossa liderança incontestável, asseguramos que todos terão a liberdade de escolher aquilo que é certo — que por sorte é exatamente o que determinamos como certo. Assim, a felicidade e a paz florescerão sob a luz da obediência.
5. Impostos (ou Dividends, como Preferimos Chamar)
Sob nosso sistema, impostos serão substituídos por "dividends". Você não será mais tributado; você estará "investindo" na sua própria liberdade. Cada centavo vai para reforçar o poder que nos mantém unidos, fortes e livres (de escolher de novo).
6. Propriedade Privada Coletiva
A propriedade é um direito absoluto. Mas para garantir seu direito, coletivizaremos todas as propriedades, deixando cada cidadão como "co-proprietário" sob nosso regime de proteção. Afinal, quem precisa de títulos de posse quando se tem a confiança do Estado?
7. Nosso Lema: "Matou Foi Pouco"
Em nossa sociedade ideal, temos um compromisso firme com a disciplina e a ordem. Se alguém questiona o bem maior que estabelecemos, lembremos todos do lema que norteia nossos valores: matou foi pouco! Aqui, não toleramos meias-medidas. Quando se trata de proteger nosso futuro perfeito, sempre podemos fazer mais — afinal, só o rigor garante que a liberdade seja plena e inquestionável.
Junte-se a Nós!
Levante-se, consumidor revolucionário! Sob a bandeira do Stancap, você será livre para obedecer, livre para consumir e livre para estar do lado certo da história. Nossa liberdade, nossa obediência, e nossa prosperidade são uma só. Porque afinal, nada diz liberdade como um Gulag Privado™!
-
 @ 00a30478:ff07f086
2024-11-09 15:39:26
@ 00a30478:ff07f086
2024-11-09 15:39:26testing blog
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ b4403b24:83542d4e
2024-11-08 13:03:32
@ b4403b24:83542d4e
2024-11-08 13:03:32I recently came across a funny Star Wars themed meme which I couldn't resist to post here with a message
@DarthCoin vs no/shit coiners
P.S.: Sorry in advance if some of you find it as disturbing or vulgar
originally posted at https://stacker.news/items/758857
-
 @ 00a30478:ff07f086
2024-11-09 15:34:08
@ 00a30478:ff07f086
2024-11-09 15:34:08testing blog
-
 @ b4403b24:83542d4e
2024-11-08 11:46:54
@ b4403b24:83542d4e
2024-11-08 11:46:54To my great surprise, when I checked my SN notification feed today, I found out 👇
To be honest, I don't know what I did to earn it, what it means or gives me or whether I can loose it (similar to the cowboy's hat maybe @k00b can give more insights) but I am pretty satisfied adding it under my belt. 🎉
I'll keep my activity high hoping I'll find the other cowboy collectible I miss - the pistol
originally posted at https://stacker.news/items/758749
-
 @ ec42c765:328c0600
2024-10-21 07:42:48
@ ec42c765:328c0600
2024-10-21 07:42:482024年3月
フィリピンのセブ島へ旅行。初海外。

Nostrに投稿したらこんなリプライが
nostr:nevent1qqsff87kdxh6szf9pe3egtruwfz2uw09rzwr6zwpe7nxwtngmagrhhqc2qwq5
nostr:nevent1qqs9c8fcsw0mcrfuwuzceeq9jqg4exuncvhas5lhrvzpedeqhh30qkcstfluj
(ビットコイン関係なく普通の旅行のつもりで行ってた。というか常にビットコインのこと考えてるわけではないんだけど…)
そういえばフィリピンでビットコイン決済できるお店って多いのかな?
海外でビットコイン決済ってなんかかっこいいな!
やりたい!
ビットコイン決済してみよう! in セブ島
BTCMap でビットコイン決済できるところを探す
本場はビットコインアイランドと言われてるボラカイ島みたいだけど
セブにもそれなりにあった!

なんでもいいからビットコイン決済したいだけなので近くて買いやすい店へ
いざタピオカミルクティー屋!

ちゃんとビットコインのステッカーが貼ってある!

つたない英語とGoogle翻訳を使ってビットコイン決済できるか店員に聞いたら
店員「ビットコインで支払いはできません」
(えーーーー、なんで…ステッカー貼ってあるやん…。)
まぁなんか知らんけどできないらしい。
店員に色々質問したかったけど質問する英語力もないのでする気が起きなかった
結局、せっかく店まで足を運んだので普通に現金でタピオカミルクティーを買った
タピオカミルクティー
話題になってた時も特に興味なくて飲んでなかったので、これが初タピオカミルクティーになった
法定通貨の味がした。

どこでもいいからなんでもいいから
海外でビットコイン決済してみたい
ビットコイン決済させてくれ! in ボラカイ島
ビットコインアイランドと呼ばれるボラカイ島はめちゃくちゃビットコイン決済できるとこが多いらしい
でもやめてしまった店も多いらしい
でも300もあったならいくつかはできるとこあるやろ!
nostr:nevent1qqsw0n6utldy6y970wcmc6tymk20fdjxt6055890nh8sfjzt64989cslrvd9l
行くしかねぇ!
ビットコインアイランドへ
フィリピンの国内線だぁ

``` 行き方: Mactan-Cebu International Airport ↓飛行機 Godofredo P. Ramos Airport (Caticlan International Airport, Boracay Airport) ↓バスなど Caticlan フェリーターミナル ↓船 ボラカイ島
料金: 飛行機(受託手荷物付き) 往復 21,000円くらい 空港~ボラカイ島のホテルまで(バス、船、諸経費) 往復 3,300円くらい (klookからSouthwest Toursを利用)
このページが色々詳しい https://smaryu.com/column/d/91761/ ```
空港おりたらSouthwestのバスに乗る
事前にネットで申し込みをしている場合は5番窓口へ

港!

船!(めっちゃ速い)

ボラカイついた!

ボラカイ島の移動手段
セブの移動はgrabタクシーが使えるがボラカイにはない。
ネットで検索するとトライシクルという三輪タクシーがおすすめされている。
 (トライシクル:開放的で風がきもちいい)
(トライシクル:開放的で風がきもちいい)トライシクルの欠点はふっかけられるので値切り交渉をしないといけないところ。
最初に300phpくらいを提示され、行き先によるけど150phpくらいまでは下げられる。
これはこれで楽しい値切り交渉だけど、個人的にはトライシクルよりバスの方が気楽。
Hop On Hop Off バス:
https://www.hohoboracay.com/pass.php
一日乗り放題250phpなので往復や途中でどこか立ち寄ったりを考えるとお得。
 バスは現金が使えないので事前にどこかでカードを買うか車内で買う。
バスは現金が使えないので事前にどこかでカードを買うか車内で買う。私は何も知らずに乗って車内で乗務員さんから現金でカードを買った。
バスは狭い島内を数本がグルグル巡回してるので20~30分に1本くらいは来るイメージ。
逆にトライシクルは待たなくても捕まえればすぐに乗れるところがいいところかもしれない。
現実
ボラカイ島 BTC Map
 BTC決済できるとこめっちゃある
BTC決済できるとこめっちゃあるさっそく店に行く!
「bitcoin accepted here」のステッカーを見つける!
店員にビットコイン支払いできるか聞く!
できないと言われる!
もう一軒行く
「bitcoin accepted here」のステッカーを見つける
店員にビットコイン支払いできるか聞く
できないと言われる
5件くらいは回った
全部できない!
悲しい
で、ネットでビットコインアイランドで検索してみると
旅行日の一か月前くらいにアップロードされた動画があったので見てみた
要約 - ビットコイン決済はpouch.phというスタートアップ企業がボラカイ島の店にシステムを導入した - ビットコインアイランドとすることで観光客が10%~30%増加つまり数百~千人程度のビットコインユーザーが来ると考えた - しかし実際には3~5人だった - 結果的に200の店舗がビットコイン決済を導入しても使われたのはごく一部だった - ビットコイン決済があまり使われないので店員がやり方を忘れてしまった - 店は関心を失いpouchのアプリを消した
https://youtu.be/uaqx6794ipc?si=Afq58BowY1ZrkwaQ
なるほどね~
しゃあないわ
聖地巡礼
動画内でpouchのオフィスだったところが紹介されていた
これは半年以上前の画像らしい

現在はオフィスが閉鎖されビットコインの看板は色あせている
 おもしろいからここに行ってみよう!となった
おもしろいからここに行ってみよう!となったで行ってみた
看板の色、更に薄くなってね!?

記念撮影
 これはこれで楽しかった
これはこれで楽しかった場所はこの辺
https://maps.app.goo.gl/WhpEV35xjmUw367A8
ボラカイ島の中心部の結構いいとこ
みんな~ビットコイン(の残骸)の聖地巡礼、行こうぜ!
最後の店
Nattoさんから情報が
なんかあんまりネットでも今年になってからの情報はないような…https://t.co/hiO2R28sfO
— Natto (@madeofsoya) March 22, 2024
ここは比較的最近…?https://t.co/CHLGZuUz04もうこれで最後だと思ってダメもとで行ってみた なんだろうアジア料理屋さん?

もはや信頼度0の「bitcoin accepted here」

ビットコイン払いできますか?
店員「できますよ」
え?ほんとに?ビットコイン払いできる?
店員「できます」
できる!!!!
なんかできるらしい。
適当に商品を注文して
印刷されたQRコードを出されたので読み取る
ここでスマートに決済できればよかったのだが結構慌てた
自分は英語がわからないし相手はビットコインがわからない
それにビットコイン決済は日本で1回したことがあるだけだった
 どうもライトニングアドレスのようだ
どうもライトニングアドレスのようだ送金額はこちらで指定しないといけない
店員はフィリピンペソ建ての金額しか教えてくれない
何sats送ればいいのか分からない
ここでめっちゃ混乱した
でもウォレットの設定変えればいいと気付いた
普段円建てにしているのをフィリピンペソ建てに変更すればいいだけだった
設定を変更したら相手が提示している金額を入力して送金
送金は2、3秒で完了した
やった!
海外でビットコイン決済したぞ!
ログ

PORK CHAR SIU BUN とかいうやつを買った
 普通にめっちゃおいしかった
普通にめっちゃおいしかったなんかビットコイン決済できることにビビッて焦って一品しか注文しなかったけどもっと頼めばよかった
ここです。みなさん行ってください。
Bunbun Boracay
https://maps.app.goo.gl/DX8UWM8Y6sEtzYyK6
めでたしめでたし
以下、普通の観光写真
セブ島
ジンベエザメと泳いだ

スミロン島でシュノーケリング

市場の路地裏のちょっとしたダウンタウン?スラム?をビビりながら歩いた

ボホール島
なんか変な山

メガネザル

現地の子供が飛び込みを披露してくれた

ボラカイ島
ビーチ


夕日

藻

ボラカイ島にはいくつかビーチがあって宿が多いところに近い南西のビーチ、ホワイトビーチは藻が多かった(時期によるかも)
北側のプカシェルビーチは全然藻もなく、水も綺麗でめちゃくちゃよかった

プカシェルビーチ



おわり!
-
 @ 361d3e1e:50bc10a8
2024-11-09 15:12:52
@ 361d3e1e:50bc10a8
2024-11-09 15:12:52https://forex-strategy.com/2024/11/09/which-is-the-choice-of-european-citizens-trump-or-harris/ Which is the choice of European citizens Trump or Harris? In some of the states the choice is almost 100% for one of the candidates.
europe #politics #usa #trump #harris
-
 @ 6bcc27d2:b67d296e
2024-10-21 03:54:32
@ 6bcc27d2:b67d296e
2024-10-21 03:54:32yugoです。 この記事は「Nostrasia2024 逆アドベントカレンダー」10/19の分です。Nostrasiaの当日はリアルタイムで配信を視聴していました。Nostrを使ってアプリケーションの再発明をすべきという発表を聴き、自分だったらどんなものを作ってみたいかを考えて少し調べたり試みたりしたのでその記録を書きます。また、超簡単なものですがおそらく世界初となるvisionOS対応のNostrクライアントをつくってみたので最後の方に紹介します。
アプリケーションを再発明する話があったのは、「What is Nostr Other Stuff?」と題したkaijiさんの発表でした。
Nostrプロトコルを使って既存のアプリケーションを再発明することで、ユーザ体験を損なわずにゆるやかな分散を促すことができ、プロトコルとしてのNostrも成長していくというような内容でした。
自分はまだNostrで何かをつくった経験はなかったので、実装に必要な仕様の知識がほとんどない状態からどのようなアプリケーションをつくってみたいかを考えました。
最初に思いついたのは、Scrapboxのようなネットワーク型のナレッジベースです。自分は最近visionOS勉強会をやっており、勉強会でナレッジを共有する手段としてScrapboxの導入を検討していました。
Nostrコミュニティにも有志によるScrapboxがありますが、Nostrクライアントがあればそれを使うだろうから同じくらいの実用性を備えたクライアントはまだ存在しないのではないかという見立てでした。
長文投稿やpublic chatなどの機能を組み合わせることで実現できるだろうか。そう思っていた矢先、NIP-54のWikiという規格があることを知りました。
https://github.com/nostr-protocol/nips/blob/master/54.md
まだちゃんとは読めていないですが、Scrapboxもwikiソフトウェアだし参考になりそうと思っています。正式な仕様に組み込まれていないようで、採用しているクライアントはfiatjafによるリファレンス実装(?)のwikistrくらいしか見つかりませんでした。
Scrapboxのようなナレッジベースを志向するNostrクライアントがあれば、後述するvisionOS対応クライアントの存在もありアカウントを使いまわせて嬉しいので試してみたいです。もし他にも似たようなサービスをどなたか知っていたら教えてください。
また現在は、勉強会やワークショップ、ハッカソンなどのコラボレーションワークを支援するためのツールを自分たちでも開発しています。Apple Vision Proに搭載されているvisionOSというプラットフォームで動作します。
https://image.nostr.build/14f0c1b8fbe5ce7754825c01b09280a4c22f87bbf3c2fa6d60dd724f98919c34.png
この画面で自分が入りたいスペースを選んで共有体験を開始します。
スライドなどのコンテンツや自らのアバターを同期させることで、遠隔地にいてもまるでオフラインかのように同じ空間を共有することが可能になります。
https://image.nostr.build/cfb75d3db2a9b9cd39f502d6426d5ef4f264b3d5d693b6fc9762735d2922b85c.jpg
ということなので、急遽visionOS対応のクライアントを作ってみました。検索しても1つも事例が出てこなかったので多分まだ世界で実装しているアプリはないのではないでしょうか。
とはいえ、クライアントを名乗っているもののまだ大した機能はなく、リレーからデータを取得するだけの読み取り専用です。
https://image.nostr.build/96e088cc6a082528682989ccc12b4312f9cb6277656e491578e32a0851ce50fe.png
画像では自分のプロフィールデータをリレーから取得しています。
まだどのライブラリもvisionOSに対応していなかったりで手こずったものの仕様の勉強になりました。
ただvisionOSアプリはiOSアプリ同様NIP-7が使えないので秘密鍵を自分で保管しなくてはならず、今後どう対処すべきかわかりかねています。これから時間ある時に少しずつ調べていこうと思っていますが、ネイティブアプリの秘密鍵周りはあまりリソースが多くないようにも感じました。もしどなたかその辺の実装に詳しい方いたら教えていただけると嬉しいです。
準備ができたらそのうちコードも公開したいと思っています。
これから少しずつ色んな機能を実装しながらNostrで遊んでいきたいです!
-
 @ bcea2b98:7ccef3c9
2024-11-07 18:43:30
@ bcea2b98:7ccef3c9
2024-11-07 18:43:30If you could accomplish one major goal, what would it be? Why does it matter to you, and how would it change your life or the lives of others?
My ultimate goal is to be part of a mission to Mars one day. I’ve always been fascinated by space exploration.
originally posted at https://stacker.news/items/757861
-
 @ eac63075:b4988b48
2024-10-26 16:49:49
@ eac63075:b4988b48
2024-10-26 16:49:49The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
Podcast: https://www.youtube.com/watch?v=j7nFUxbAptc
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ 74718b83:b8204bd8
2024-11-07 11:51:14
@ 74718b83:b8204bd8
2024-11-07 11:51:14Hi guys, i thought it would be interesting to compare some basic cost of living stats among stackers and ask, how hard is it to hit your basic number?
for me, in Bulgaria with 2 kids , to be comfortable, NOT in the capital , about 2k euros is a number that works for my family. i could reduce that number by up to 1000 euro if my kids didn't go to a private school. also worth noting is i own the house so have no rent or mortgage. if i was renting or had a mortgage, i would simply pay that instead of doing private school, so the number would be similar.
bills are cheap, maybe 10 euro water per month and about 40 euro electricity (this will vary though )
finding a job that pays 2k euros is quite hard outside of the capital city, even if you are a software programmer.
i manage to hit this freelancing, and it's ok, i have a 10x higher lifestyle than i would in the UK and i own a property etc . the downside is a client will randomly leave etc and it puts a lot more strain on the budget, the upside is i am at least the master of my time, which i find very valuable
originally posted at https://stacker.news/items/757311
-
 @ b184e3ed:27924b0d
2024-11-07 03:06:37
@ b184e3ed:27924b0d
2024-11-07 03:06:37When I joined AA, this question started to haunt my thoughts during those frequent nighttime anxiety attacks. Among all the chaos in my life, there were a few things I was certain of. And one of those things was the certainty of never having felt God, I didn't even know that God was something you could feel. For me, when I started the 12-step program, God was a social construct, something humans had invented to control a society thirsty for basic survival instincts. And perhaps I wasn't so wrong, but like everything in life, this was only half the truth. Despite my deep cognitive analysis that my anxiety forced me to do almost every night for hours, often until the first ray of sun pierced my bedroom window, my spiritual bias didn't allow me to see the whole picture, or a complete reality. On that side, there had always been a void Later, I realized that this emptiness was the main cause of all my problems. From there came that feeling of always being incomplete, that anxiety of always feeling like something was missing, that need to always want to fill voids that weren't mine, without realizing that it was only creating more emptiness within me Once, in those heart-to-heart talks that we in AA call sponsorship, my soul expressed the painful doubt, 'What does it mean to feel God?' My sponsor simply replied, 'I assure you that when you feel God, you won't doubt that what you feel is God. There is no doubt in matters of God. And so I left, with that answer that left me right where I started. And with more doubts. Why is there no doubt in matters of God?
After thinking about it for so long, I paused for a few seconds. I closed my eyes and decided, for the first time, to talk to this so-called God. I let go of all my feelings, all my disbelief, and I prepared myself to accept anything different from what I already had, because what I had wasn't working for me at all. With all sincerity and feeling a pressure in my chest, closer to my heart than usual, I asked in a low voice God, what does it feel like to feel you? What should I do to feel you? What's the manual for feeling you? I've tried everything, I don't know what else to do, what else to plan. I accept that I need to feel you. Everyone tells me that when I feel you, everything will make sense and only then will I start to let go of this violent need to consume my drug of choice. But nobody tells me how. What am I not seeing? Please, give me something. I can't take it anymore, I'm running out of strength, I'm wasting my life stuck in the same cycle. I can't do this anymore, help me feel you. Then a pain began to flow, but a particular one that every addict knows, that soul-deep pain that comes from emptiness, that pain that turns on the faucet of tears that began to flow non-stop. I allowed myself to feel that pain, everything turned dark and negative, suicidal thoughts returned, hate, resentment, selfishness, depression, all together, all that is lived in darkness, all that is felt in solitude, all that came from emptiness. And only by feeling it, could I see where that deep pain came from, I could visualize the path it left behind. For the first time, I recognized my spiritual emptiness. And it was only then that I began to see the whole picture of my life. Doubt has no place in the things of God because God is not logic, God is not reason, much less a manual. Doubt comes from logic, therefore where there is doubt, there is also an absence of God, emptiness. And right at the moment of recognizing that, very specific images came to my mind. My sponsor hugging me for the first time when I arrived and interviewed me. With that hug came the words, 'You're not alone, you're already in a safe harbor, we'll be with you from start to finish. One day at a massive AA event, right in the middle of a workshop dynamic, that deep and sincere hug my fellow sufferer and I shared, in the midst of deep crying with our eyes closed, someone guided our arms to each other. To end up keeping each other company in that darkness we had always gone through alone. That trip to a Group Anniversary outside the city, where a fellow member of my group and I were simply enjoying the scenery, the wind on our faces, and laughing at the craziness of our daily lives, this on my motorcycle on the highway. That hug it took me years to find in the arms of my younger sister, right after arriving after a writing session. That hug of forgiveness to my mother and father that I had never been able to give before because I didn't want to go through the pain that came with feeling. Those few seconds in the rain that we spent lost on our way to the new location of our Group that I experienced in the company of a fellow member. Seeing a new person arrive with a desire to start their process. Connecting in the same feeling and emotion that comes with the death of a best friend. Serving a cup of coffee to that fellow member who returns after months of absence. Arriving at the group with hope of seeing that fellow member who hasn't been coming for weeks and little is known about what happened, but they no longer come to meetings. Day after day, their chair remains empty. And then start letting go of their defenses and their craziness. Standing in front of several strangers, with my head held high, my gaze firm, saying my name and then, 'I am a drug addict. To say, 'I feel like shit, but I'm here for whatever I can contribute. To feel like I'm that support for those who were my support when I was at rock bottom. And not just feel it, but also be able to be it. And that, to mention just a few of the scenes that came to my mind, then I understood 'I had already felt God.' I wasn't lacking spirituality, I wasn't lacking God, I just needed to stay still for a moment to feel it. And to feel that he has always been there. And that he will never leave my side. So today I can answer my own question, 'That's what it feels like to feel God' but not just any God. But a very special one, the God of the 4th and 5th step addicts and alcoholics...
originally posted at https://stacker.news/items/756957
-
 @ a012dc82:6458a70d
2024-11-09 14:44:19
@ a012dc82:6458a70d
2024-11-09 14:44:19Table Of Content
-
The Petrodollar's Historical Significance
-
Challenges to the Petrodollar
-
The Emergence of Bitcoin
-
Bitcoin's Potential to Disrupt the Financial System
-
The Future of the Petrodollar and Bitcoin
-
Conclusion
-
FAQ
The global financial landscape has undergone significant transformations over the years. One of the most intriguing developments is the rise of Bitcoin and its potential impact on the traditional financial system. In this article, we will delve into the challenges faced by the petrodollar and explore the promises offered by Bitcoin as we examine the financial future.
The Petrodollar's Historical Significance
The petrodollar refers to the system in which the U.S. dollar is used as the primary currency for international oil trades. It originated in the early 1970s when an agreement was reached between the United States and Saudi Arabia. Under this agreement, oil-producing nations agreed to price their oil exclusively in U.S. dollars, and in return, the United States provided military support to these nations.
Challenges to the Petrodollar
Geopolitical Factors
Over the years, geopolitical factors have challenged the dominance of the petrodollar. The rise of new economic powers, such as China, has led to increased demand for alternatives to the U.S. dollar. As countries seek to diversify their reserves and reduce dependency on the U.S. currency, the petrodollar's position has weakened.
Currency Wars
Currency wars, characterized by competitive devaluations and trade disputes, have also put pressure on the petrodollar. In an attempt to gain a competitive advantage, countries manipulate their currencies, which can have a significant impact on the value and stability of the U.S. dollar.
Devaluation and Inflation Risks
The petrodollar's woes are further compounded by the risks of devaluation and inflation. The continuous printing of money and increasing debt levels in the United States can erode the value of the dollar over time. This potential loss of purchasing power raises concerns among countries heavily reliant on the petrodollar system.
The Emergence of Bitcoin
Understanding Bitcoin
Bitcoin, created in 2009, is a decentralized digital currency based on blockchain technology. It operates independently of any central authority, such as governments or financial institutions. Bitcoin transactions are recorded on a public ledger, providing transparency and security.
Bitcoin's Advantages
Bitcoin offers several advantages over traditional currencies. It provides a decentralized and secure system that eliminates intermediaries and reduces transaction costs. Additionally, Bitcoin's limited supply and mathematical framework make it resistant to inflationary pressures, unlike fiat currencies.
Adoption and Regulatory Landscape
The adoption of Bitcoin has been steadily growing, with individuals, businesses, and even governments exploring its potential. However, the regulatory landscape surrounding cryptocurrencies remains uncertain in many jurisdictions. Governments are grappling with the need to balance innovation and consumer protection, which poses challenges to widespread adoption.
Bitcoin's Potential to Disrupt the Financial System
Decentralization and Trust
One of Bitcoin's key promises is the concept of decentralization, where power is distributed among participants rather than concentrated in a central authority. This decentralized nature removes the need for intermediaries, such as banks, and reduces the risk of censorship, fraud, and manipulation.
Financial Inclusion
Bitcoin has the potential to improve financial inclusion by providing access to financial services for the unbanked population. With just a smartphone and an internet connection, individuals can participate in the global economy, send and receive money, and store value securely.
Security and Transparency
The blockchain technology underlying Bitcoin ensures the security and transparency of transactions. Each transaction is recorded on the blockchain, making it immutable and tamper-proof. This transparency builds trust among users and can help combat financial crimes, such as money laundering and fraud.
The Future of the Petrodollar and Bitcoin
Coexistence or Competition?
The future relationship between the petrodollar and Bitcoin remains uncertain. It is possible that both systems could coexist, with Bitcoin serving as a complementary currency rather than a direct replacement. Alternatively, increased adoption of Bitcoin could pose a challenge to the petrodollar's dominance, especially if countries diversify their reserves.
Central Bank Digital Currencies (CBDCs)
The emergence of Central Bank Digital Currencies (CBDCs) adds another layer of complexity to the financial landscape. CBDCs aim to combine the advantages of cryptocurrencies with the stability of traditional fiat currencies. The development of CBDCs could reshape the global financial system and potentially impact the petrodollar and Bitcoin.
Shifting Paradigms in Global Finance
The rise of Bitcoin symbolizes a shifting paradigm in global finance. It challenges the traditional banking system, offers new opportunities for financial inclusion, and promotes financial sovereignty. While the petrodollar has enjoyed decades of dominance, its future may depend on adapting to the changing financial landscape.
Conclusion
As the petrodollar faces challenges from geopolitical factors, currency wars, and inflation risks, Bitcoin emerges as a potential disruptor in the financial system. With its decentralized nature, advantages over traditional currencies, and growing adoption, Bitcoin offers promises of increased financial inclusion, security, and transparency. The future relationship between the petrodollar and Bitcoin remains uncertain, but their coexistence or competition will shape the financial landscape in the years to come.
FAQs
Is Bitcoin legal? Yes, the legality of Bitcoin varies from country to country. While some nations have embraced cryptocurrencies and established regulatory frameworks, others have imposed restrictions or bans.
Can Bitcoin be hacked? Bitcoin's blockchain technology makes it highly secure and resistant to hacking. However, individual wallets and exchanges can be vulnerable to cyber attacks. It is crucial to take necessary precautions, such as using reputable wallets, enabling two-factor authentication, and keeping private keys secure.
How can I buy Bitcoin? To buy Bitcoin, you can use a cryptocurrency exchange or a peer-to-peer trading platform. These platforms allow you to convert fiat currency (such as USD) into Bitcoin. It is advisable to choose a reputable and regulated exchange, conduct thorough research, and follow best security practices when buying and storing Bitcoin.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-07 01:50:21
@ 5d4b6c8d:8a1c1ee3
2024-11-07 01:50:21I'm watching the Warriors laying it on the Celtics and I'm struck by how uniquely fun to watch Steph still is.
If you were picking a team of who you're most enjoying this season, who would be in the starting five?
Here's my most entertaining starting 5 (ordered by position, not entertainingness): 1. Lamelo 2. Steph 3. Ant 4. Chet 5. Jokic
originally posted at https://stacker.news/items/756861
-
 @ 1eb966a6:e3eddf94
2024-11-09 13:19:43
@ 1eb966a6:e3eddf94
2024-11-09 13:19:43eyJfaWQiOiJhNThkNzNlMi05NzAwLTQ3ZmUtODZiMy0xZGU0NWQwZGRhZDIiLCJwdWJsaWNLZXkiOiIxZWI5NjZhNmEwMjE4YWJhNTIwYWFhYzkzYmU3ZGQ4YmYzODMwZmM3NzEwYmM4MGNhZWEzYTZhNWUzZWRkZjk0IiwidXNlcm5hbWUiOiJoYW5rIiwiYWRUeXBlIjoiTE9DQUxfU0VMTCIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIG9mIEFtZXJpY2EiLCJjb3VudHJ5Q29kZSI6IlVTIiwibGF0IjozNC4wNTM2OTEsImxvbiI6LTExOC4yNDI3NjYsImdlY29kZSI6eyJwbGFjZV9pZCI6Mjg0ODczMDQ4LCJsaWNlbmNlIjoiRGF0YSDCqSBPcGVuU3RyZWV0TWFwIGNvbnRyaWJ1dG9ycywgT0RiTCAxLjAuIGh0dHBzOi8vb3NtLm9yZy9jb3B5cmlnaHQiLCJvc21fdHlwZSI6InJlbGF0aW9uIiwib3NtX2lkIjo2MzMzMTQ1LCJsYXQiOiIzNC4wNTM2OTYwNSIsImxvbiI6Ii0xMTguMjQyOTIxMjE4MzMzOTUiLCJkaXNwbGF5X25hbWUiOiJMb3MgQW5nZWxlcyBDaXR5IEhhbGwsIDIwMCwgTm9ydGggU3ByaW5nIFN0cmVldCwgQ2l2aWMgQ2VudGVyLCBEb3dudG93biwgTG9zIEFuZ2VsZXMsIExvcyBBbmdlbGVzIENvdW50eSwgQ2FsaWZvcm5pYSwgOTAwMTIsIFVuaXRlZCBTdGF0ZXMiLCJhZGRyZXNzIjp7ImJ1aWxkaW5nIjoiTG9zIEFuZ2VsZXMgQ2l0eSBIYWxsIiwiaG91c2VfbnVtYmVyIjoiMjAwIiwicm9hZCI6Ik5vcnRoIFNwcmluZyBTdHJlZXQiLCJxdWFydGVyIjoiQ2l2aWMgQ2VudGVyIiwic3VidXJiIjoiRG93bnRvd24iLCJjaXR5IjoiTG9zIEFuZ2VsZXMiLCJjb3VudHkiOiJMb3MgQW5nZWxlcyBDb3VudHkiLCJzdGF0ZSI6IkNhbGlmb3JuaWEiLCJJU08zMTY2LTItbHZsNCI6IlVTLUNBIiwicG9zdGNvZGUiOiI5MDAxMiIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIiwiY291bnRyeV9jb2RlIjoidXMifSwiYm91bmRpbmdib3giOlsiMzQuMDUzMDE0MSIsIjM0LjA1NDM3MTMiLCItMTE4LjI0MzUzIiwiLTExOC4yNDIwMDUyIl19LCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjowLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsIm1zZyI6Im1lZXQgbWUgb25seSBpbiBwdWJsaWMiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMDg6NTI6MjYuNzkzWiIsIm1hcmtldFByaWNlIjoxNjIuMTd9
-
 @ e968e50b:db2a803a
2024-11-06 21:10:16
@ e968e50b:db2a803a
2024-11-06 21:10:16https://youtu.be/vAM8rcmb4oQ?si=qpnJHtoVhLyG4Mek
originally posted at https://stacker.news/items/756531
-
 @ 1bda7e1f:bb97c4d9
2024-10-24 04:48:52
@ 1bda7e1f:bb97c4d9
2024-10-24 04:48:52Tldr
- Nostr relays help users post and read notes on the network
- Relay operators have launched a variety of relays for you to use
- You too can launch your own relay for any reason you like
- Launching your own relay gives you a lot of power in how you use Nostr
- Many relay softwares exist for you to use
- I launched a personal relay using HAVEN relay software on my VPS
- I am now more in control of saving notes, cutting spam, and protecting my privacy
- My personal relay is now hosted at relay.rodbishop.nz
What are Nostr Relays Anyway?
When you're a user of a social network, you post and read notes from other users on the network. In a centralised network like Twitter or Instagram the company's servers receive all user's notes and relay them to other users. On Nostr, there is no single company's servers to relay messages, so instead the task is taken up by relay operators.
Anyone can be a relay operator and they can run a relay for any purpose. When you start using Nostr you will usually be connected to any one of a number of "public" relays, and be able to post and receive notes from users on the network via these.
Configuring these relays can tailor your experience somewhat–for example the client Nostrudel allows you to select from Western or Japanese relay set.
It is also possible to set up your own relay to use for your own purposes. All kinds of people have launched relays for all kinds of purposes. For example, to:
- Power your own client
- Support your community
- Run a for-profit relay business
- Relay a certain a type of content you need
- Back up your own notes, decrease spam, or increase privacy
- Curate your own social feed with your own algorithm
Relay instances available to connect with
Today is an interesting time in relay-ops. The evolution of the technology has inspired users to experiment with diverse types of relays tailored to various needs. As a result there are very many relay instances in operation and available to connect with.
A few sites try to collate which relays are in operation, like nostr.info and xport.top and sesseor's relay list . These lists are long (Sessor's list counted 2,500+ relays) and it's not clear to me whether it's even possible to be comprehensive as relays may join or leave the network all the time.
Broadly speaking, relays might be available for different users to use in different ways:
- A relay where anyone can post, like relay.damus.io
- A paid relay where anyone can post after payment, to cut spam, like nostr.wine
- A "web of trust" relay where anyone can post if they are related to the owner's social graph, to cut spam, like nostrelites.org
- A speciality relay where a particular community can post, like nostr.com.au for #austriches (Australians)
- A relay where anyone can post just specific content, like purplepag.es for user profiles only
- A team relay for your company or organisation only
- A personal relay for your own personal use
Nostr.Band shows which of these available relays are most popular, such as relay.damus.io and nos.lol and eden.nostr.land
Relay softwares for you to launch your own
You may decide to launch you own relays, and if you do there are many different relay softwares to choose from:
- Simple, like Bucket (<100 lines of code)
- Widely used, like Nostream (top ranked on Github)
- Customisable, like Khatru (a framework for customised relays)
- Specialised, like HAVEN or Team Relay (for personal or teams relays, based on Khartu)
You can run these on your own server, or local machine, or phone or with a third-party host.
Aljaz provides a great resource with 45+ relay softwares to choose from.
In summary, at a high level,
- Anyone can connect to any of the relay instances that are available for them to use
- Anyone who wants to launch their own can select the relay software that best suit their needs, launch an instance, and have it used by whichever users they like
Reasons to Run Your Own Relay
As a normal user of a Nostr client there's no obligation to run a relay. But having your own relay does give you more power.
For my own journey down the #nostr rabbit hole, I was looking for a relay to:
- back up my notes
- decrease spam
- increase my privacy
- learn skills I could later use for running a community or team or paid relay
Backing up notes – When you post notes to a public relay there's no guarantee that the relay is going to keep them long-term. It's job is relaying your notes to other clients, not storing them. Running your own relay allows you to keep your notes online.
Decrease spam – To first spam we can use a "Web of Trust" model–in which users endorse other users as trustworthy. A "Web of Trust" relay will reject notes from parties too far removed from your network. Running your own relay makes you more difficult to spam.
Increasing privacy – When you connect to a public relay, they can determine personal information about you, such as your IP address. Running your own relay keeps things more private.
For communities and teams and paid relays – Many opportunities exist to tailor relays to certain users needs, be they businesses or communities or as a for-profit business. For me, I am hoping that running my own relay helps me learn skills I can use in these kinds of further ventures.
To start I decided to focus on a personal relay. However, when I really got under the hood, it turned out I would need multiple relays not just one.
The outbox model
Mike Dilger proposed the outbox model (originally called the gossip model) as a way for users to engage with the wider Nostr network. It's a great model that is helpful to understand, as it suggests to establish different relays for different purposes.
Many clients and relay softwares have now adopted and continued to elaborate on this model. An example is to run specialised relays for Outbox, Inbox, Chat and Private needs.
Outbox Relay (also called Home Relay)
- This relay is for notes you have written, so that everyone knows where to find your notes
- In a set up where you are running your own, this relay is restricted so that only you can post to it, and you should set up your clients to post your notes to it
- An advanced version may take any notes received to this relay and "blast" them to other public relays so that your notes get wider reach
Inbox Relay (also called Public Relay)
- This relay is for public notes that other users want you to see, so that you always find notes that are relevant to you, including all replies, comments, likes, and zap payments
- In a set up where you are running your own, this relay is where you should look for notes relevant to you, and you should set up your clients to read from it
- An advanced version may search other public relays for notes that tag you, and import them into this relay so that you never miss a relevant note
Chat Relay (also called Direct Message Relay)
- This relay is for private direct message notes from other users, so that you always find your direct messages and so that they stay private
- In a set up where you are running your own, this relay is restricted so that only you can read from it, and you should set up your clients to read from it
- An advanced version may cut spam by only accepting direct messages from other users within your Web of Trust
Private Relay
- This relay is for your private use only, so that you can store private drafts or thoughts
- Only you can write to it and only you can read from it (and so, it is a bit mis-named as it does not actually relay anything to anywhere at all)
- In a set up where you are running your own, it gives you true privacy for these notes
In summary as a user
- I post my notes to my outbox relay. Network users can read them there, and if the relay is advanced it will also blast the notes out to other relays on the network
- I read from my inbox relay. Network users know to reach me there, and if the relay is advanced it will also bring me notes from the wider network
- I can have private direct message conversations with others in my chat relay.
- I can save private notes in my private relay
For me, this model has a lot of appeal and I went looking for a personal relay which adopted this model and contained all of these features.
HAVEN as a personal relay
I decided to go with HAVEN relay software.
HAVEN is all four of the above relays in one–outbox, inbox, chat and private. It contains advanced features like blasting your notes from outbox to other relays, importing notes from other relays to your inbox, and preventing spam with Web of Trust.
HAVEN is written by Utxo the Webmaster . It is based upon the Khatru relay framework by Fiatjaf
Setting up HAVEN as a Personal Relay
I am mostly non-technical, but on my #Nostr journey I have been having success with technology set ups that use Docker.
- I have a cheap VPS which currently runs Albyhub and Phoneixd with Docker,
- My objective was to set up HAVEN to run alongside it, in a separate Docker on the same server. HAVEN does not include Docker by default, but Sebastix published a fork with Docker support.
To get HAVEN up and running in Docker on your VPS:
- Clone and configure HAVEN with the right variables
- Launch it in Docker on your VPS
- Check the URLs and logs to see your HAVEN running
- Configure a subdomain to point to the VPS
- Configure the VPS to reverse proxy to the Docker port
- Configure the relays in your favourite Nostr client
- Post a note to your outbox and see if it blasts!
Running HAVEN
I cloned Sebastix fork to start.
git clone -b docker_compose_support https://github.com/nostrver-se/haven.git cd havenThe software sets up all environment variables in the
.envfile, and comes with an.env.examplefile. Duplicate and rename the file to.env. Within the.envfile you need to set up the environment variables. The file is long but it contains lots of repetition and for the most part defaults can be retained–only a few changes are required:- Replace all instances of the default user npub with your own (for me,
npub1r0d8...) - Change the default relay URL to your own (for me,
relay.rodbishop.nz) - Replace all instances of the default name in the relay names (for me, "Rod's ...")
- Replace all instances of the default profile image with your own
To enable automatic blasting from your outbox, and importing to your inbox, the software comes with an example list of relays to blast and import from. See
relays_blastr.example.jsonandrelays_import.example.json. To use these features simply duplicate and rename these files torelays_blastr.jsonandrelays_import.jsonrespectively. Within these files you can specify the public relays of your choice. I simply used the default list.There are other features available, such as backups and initial imports, but I decided to handle these later. To start with I wanted to launch the relay and test it.
To launch the relay run Docker Compose.
docker-compose up -d docker logs haven-relayThen you should explore the logs in the command line and the ports in your browser to see if it launched successfully. The logs should show your web of trust has been built successfully and the browser should show simple landing pages.
The logs should show that the relay has queried the network and built a web of trust from your followers. Mine looked as follows.
2024/10/14 12:02:08 🌐 building web of trust graph 2024/10/14 12:02:16 🫂 total network size: 13296 2024/10/14 12:02:16 🔗 relays discovered: 335 2024/10/14 12:02:17 🌐 pubkeys with minimum followers: 9394 keysYour browser should show you have four relays in operation, for example as follows.
your_IP_address:3355(your outbox or home relay)your_IP_address:3355/private(your private relay)your_IP_address:3355/chat(your direct message relay)your_IP_address:3355/inbox(your inbox relay)
That's it. Your relay is online.
Connecting HAVEN
Now all that remains is the plumbing to connect your domain, relay, and Nostr clients together.
Configure DNS
First, configure your domain. At a high level –
- Get your domain (buy one if you need to)
- Get the IP address of your VPS
- In your domain's DNS settings add those records as an A record to the subdomain of your choice, e.g.
relayas inrelay.your_domain_name.com, or in my caserelay.rodbishop.nz
Your subdomain now points to your server.
Configure reverse proxy
Next, you need to redirect traffic from your subdomain to your relay at port
3355.On my VPS I use Caddy as a reverse proxy for a few projects, I have it sitting in a separate Docker network. To use it for my HAVEN Relay required two steps. I am sure that the way I do this is not very elegant, but it worked. If you prefer a different method, the HAVEN readme also comes with instructions on how to perform a similar setup using nginx.
For my method, my steps were as follows:
- Add configuration to Caddy's
Caddyfileto tell it what to do with requests for therelay.rodbishop.nzsubdomain - Add the Caddy Docker network to the HAVEN
docker-compose.ymlto make it be part of the Caddy network
For the addition to the
Caddyfile, I used as follows:relay.rodbishop.nz { reverse_proxy haven-relay:3355 { header_up X-Forwarded-For {remote} header_up X-Forwarded-Proto {scheme} header_up X-Forwarded-Port {server_port} } }For the addition to the
docker-compose.yml, I used as follows:``` networks: - caddy # Added this line to services to connect to the Caddy network
networks: caddy: external: true # Added this to section specify the Caddy network ```
Once your DNS configuration and reverse proxy setup are completed, you should now be able to access your Nostr client at
relay.your_domain_name.com. For my set up, this wasrelay.rodbishop.nz.Connecting your Nostr client
Most Nostr clients allow you to specify any relay you choose. My go-to client at the moment is Amethyst on Android. Amethyst allows you to specify discrete relays for each role in the outbox model which ties up very neatly with HAVEN.
- In the sidebar, select Relays
- For "Public Outbox/Home Relays" enter
relay.your_domain_name.com - For "Public Inbox Relays" enter
relay.your_domain_name.com/inbox - For "DM Inbox Relays" enter
relay.your_domain_name.com/chat - For "Private Home Relays" enter
relay.your_domain_name.com/private - Click Save to broadcast your new relays to the Nostr network.
Your new relay configuration is now live.
Testing your relay
Lastly, it's time to test. Amethyst provides a simple method to test this as it allows you to configure the relays used on each post.
- Create a test note, and then before you post it, edit your relays using the icon at the top
- Turn off all relays except your own outbox relay, and post the note
- Access your HAVEN docker logs with
docker logs haven-relayand see if there is a log to indicate if the note was received and blasted to other public relays - Copy the
neventof the note, and attempt to find it in another client
If you're in luck, you may see something like this (the blasted note, and then users on the network responding to the note in turn).
2024/10/22 00:12:23 🔫 blasted 95c477af7e6b612bf5d1d94309d2d57377a0a67d2181cfbb42a2e3fbc0feeaaf to 26 relays 2024/10/22 00:13:50 🤙 new reaction in your inbox 2024/10/22 00:14:42 🫂 new reaction in your inbox 2024/10/22 00:14:45 ✅ new reaction in your inbox 2024/10/22 00:15:12 💜 new reaction in your inbox 2024/10/22 00:17:03 ✅ new reaction in your inbox 2024/10/22 00:17:03 🫂 new reaction in your inbox 2024/10/22 00:17:55 🫂 new reaction in your inbox 2024/10/22 00:19:02 📰 new note in your inboxThat's it. If you followed this successfully your personal relay is up and running.
What I did wrong so you don't have to
My first relay was too public
This blog comes after much trial and error. The first error I made was I set up a relay to use as a personal relay, but without any restrictions on use. I very quickly found other people discovered and started using my relay to save their own notes! This was unintended and I had to take it down.
Unfamiliar with Go language
I am mostly non-technical, and completely unfamiliar with Go. I got the project up and running with Go on my localhost–with a lot of help from my AI–but I then completely failed in migrating this to my VPS. Moving to Docker made the difference for me here.
I failed a few times due to a messy folder
After messing with Go, I moved to the Docker setup, but I started my work from a messy folder which contained remnants of the Go build, which caused various failures. Deleting the folder and cloning again from scratch solved the issue.
Trouble with Nostr.wine
I subscribe to the Nostr.wine paid relay, and I initially added it to the list of relays in my blaster. However, it didn't work, and the logs showed an error as follows
CLOSED from wss://nostr.wine: 'auth-required: this relay only serves private notes to authenticated users'It seems my npub's subscription to Nostr.wine is not enough for it to permit my relay to blast notes to it. In the end, I removed Nostr.wine from my relay config, and kept Nostr.wine as a separate entry in my Client's outbox settings.
Failed to create web of trust graph
When I first launched the relay on my VPS, HAVEN failed to complete the Web of Trust graph, with a log that looked as follows (note the zeroes). As a result, no one would have been able to send me DM's to my Chat relay (it would flag every message as spam).
2024/10/14 12:02:08 🌐 building web of trust graph 2024/10/14 12:02:16 🫂 total network size: 0 2024/10/14 12:02:16 🔗 relays discovered: 0 2024/10/14 12:02:17 🌐 pubkeys with minimum followers: 0 keysI never got to the bottom of why this was. In the process of trying to fix it I rebuild the container, and on the rebuild it spontaneously worked. Accordingly my lesson learned is "if in doubt, turn if off and on again".
Failed to run --import function
HAVEN comes with a function to import all your old notes from other public relays to your own outbox relay. When I run it I get an error as follows:
panic: Cannot acquire directory lock on "db/private". Another process is using this Badger database. error: resource temporarily unavailableI have yet to work out the solution for this, and will update this note when I do so!
What's Next?
Over the past four blogs I have
- Mined a Nostr pubkey and backed up the mnemonic
- Set up Nostr payments with a Lightning wallet plus all the bells and whistles
- Set up NIP-05 and Lighting Address at my own domain
- Set up a Personal Relay at my own domain
This feels like a very comprehensive personal set up now. Also, I have uncovered some new rabbit holes and feel like I have some projects to tackle. Perhaps one of these?
- Set up a personal homepage with my Nostr feed to round-out my rodbishop.nz domain
- Experiment with different signers like Amber and Nsec.app and NFC cards
- Set up a paid relay for #austriches (Australians and Kiwis on Nostr)
- Set up a team relay to experiment with Nostr for business or community projects
- Or something else ... ?
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
Pura vida Nostr.
-
 @ 101b30ee:18a46a45
2024-10-15 00:30:33
@ 101b30ee:18a46a45
2024-10-15 00:30:33背景
Junさんが山形県在住で、車で色々案内いただけることになりました。
メンバー (敬称略)
- Jun (nostr:npub1nlnjcakw6xfkpuhx9kym3d20sr774pm6rue5kk93uj7lrca9lypqgqj7fd)
- りら (nostr:npub1tuqsl6l8xzly95vv80um7wsnt7gxy8w9wgt4khp4wyv4xwhfw44slm93e9)
- あめ (nostr:npub1eqw8nx0hya3cwvtc0rje6lpjzzf6gvuh0mngz898dhp6juuwrp5s5uzduw)
- Don (nostr:npub1dv9xpnlnajj69vjstn9n7ufnmppzq3wtaaq085kxrz0mpw2jul2qjy6uhz)
- 横谷加奈子 (nostr:npub1sd2zns7qsfster7vcyjcqkert4cev2rzfeuus0d8hnfdh74t6g7su0p4c6)
- 発火大根 (nostr:npub1zqdnpm5gcfap8hngha7gcp3k363786phvs2etsvxw4nh6x9ydfzsuyk6mn)
スケジュール
10/12
11:00 - 11:30 霞城セントラル 日本酒めぐりツアー
500円で3コインもらえて、1コインでカップ1杯分の試飲ができるシステムのようです。
山形はフルーツも有名で、日本酒だけでなくワインなども試飲できました。個人的には、梨ベースのお酒が飲み口すっきりしていておいしかったです。
名前は忘れました ()霞城公園セントラル
https://yamagatakanko.com/attractions/detail_13443.html
nostr:nevent1qqszfgt4vef3ncyw7cy9yykuwv06pq5v9znaf2xeehfpp6s5j27ncqg2val6m nostr:nevent1qqsvfknrdtwsyvmztdzx40adzvtx8nztxu3vscgkljzzk2zr8kfmfnce54ke0
11:30 - 12:30 霞城公園散策
東北屈指の戦国大名・最上義光(もがみよしあき)公 (1546-1614)が礎を築いた「山形城」を復原整備した都市公園らしいです。
Junさんに聞いたところ、最上義光の妹が伊達政宗の母・義姫 (よしひめ)で、息子の伊達政宗を毒殺しようとしたことで有名らしいです。
後で調べたところ、毒殺事件が捏造だったとする記事もあり、真偽はいかに。また、これもJunさんに聞いたのですが山形藩は幕府重役から失脚した左遷の地と呼ばれているようです。
ちょっと悲しい。
後に調べたところ、山形藩は計12家が収めており、入れ替わりも激しかったようです。
まぁ、左遷だったとしても自然豊かな地でスローライフを過ごすのもアリかもしれない。個人的には、最上義光像が精巧に出来ているなぁと感動しました。
構図がナポレオンに似ていたので、もしかして身長が低かった?と思いましたが
後で調べたところ、180cm以上の長身だったとする文献があるようです。山形藩
https://ja.wikipedia.org/wiki/%E5%B1%B1%E5%BD%A2%E8%97%A9
義姫の毒殺事件について
https://bushoojapan.com/bushoo/date/2024/08/12/76725
最上義明の身長
http://iiwarui.blog90.fc2.com/blog-entry-13581.html
霞城公園セントラル
https://yamagatakanko.com/attractions/detail_2304.html
nostr:nevent1qqsp78jf76yudrwf6w88szq4x50t0zpeht77adkmk5pj5xsg6wplcmcv25e3g nostr:nevent1qqsfvw828mus5ek44m5myuya5ndpvj8mjhlltzx4y6ha93932cvzaxgwqwah3 nostr:nevent1qqs9sd8m43lj6pmd7hzu0quf4v0s7rm4uaq83aqp5jn5sqfy8aw6f8skg0sgv
12:30 - 13:30 旧済生館
済生館は1878年(明治11年)に山形県立病院として建設され、東北地方で最も早く西洋医学を取り入れたことで有名のようです。
建物内部の展示物の写真撮影は禁じられていたので写真は取れていませんが、あの有名な杉田玄白の訳書「解体新書」や、明治時代の医療器具などが展示されていました。私は工業高校出身で電気科だったので、昔の医療電気機器の展示などは見ていて飽きないものがありました。
旧済生館
https://www100.pref.yamagata.jp/110001/sangyo/sangyoushinkou/him_top/him_maincat1/him_15.html
13:30 - 14:30 山寺付近に移動・ランチ
山寺付近に車で移動後、玉こんにゃくを食べながら山寺方面に徒歩移動。
玉こんにゃくは名産らしく、山形のいたるところで売っていました。途中で近場のお店でランチ(蕎麦)を食べました。
ランチを食べながら映画 (オッペンハイマー)の話とかビットコインの話をしてました。
ちなみに私はオッペンハイマー見れてません。
あめさんはオッペンハイマーを見に県外 (奈良 -> 大阪)まで行ったらしい。
行動力すげぇ。nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpgqwakh6t2vm0ufy82rmwjqa2ld2z9jdl9l90v0ds7afwe6n5myl5uf5p7 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqq570ak2p9wx9q09xafjnlnulshwg2wc5c66q37z884m0pselu36sz5k7jk nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpp8xy7nktvyq87d676pkh6hjpftm5s703fq8e8c52l2l9xupe55wyhfc0p nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqgqthnr72cp92yqv9upzg2fyplvt6eazf6kxe24h6ea6syg3mthsl5tc3r26
14:30 - 16:00 山寺 (宝珠山立石寺)
宝珠山立石寺 (愛称:山寺)は山形屈指の観光スポットで、松尾芭蕉が「閑さや岩にしみ入る蝉の声」の名句を紀行文「おくのほそ道」に残したことでも知られているそうです。
展望台付近まで登りましたが、前日2時間程度しか寝れてなかった からか、途中で何回か力尽きました。
何気にずっと階段だったのが厳しかった。w
展望台から見る景色が超綺麗でした。達成感あった。途中でDonさんが「松尾芭蕉も山寺登ってますよ!」と励ましてくれましたが、松尾芭蕉は服部半蔵だったのでは、といわれる説が頻繁に出るくらい、体力おばけです ()
#### 山寺・宝珠山立石寺 https://yamagatakanko.com/attractions/detail_2352.html
松尾芭蕉が忍者服部半蔵ではないかと言われる都市伝説の理由5つ
https://spirituabreath.com/matuobasyou-hattorihannzou-5207.html
nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqs2jsu0efm0s0xnp9exv0m4xkxaw07nsraxhfjqrl6rmjd977aqcycfaf05e nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqsxmrsa8h6y6z8hmt7hzg8cmspvc373gnjjs67vlrdp24lud8wm8ncp682ev nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqgq3a6ehlurcsmpzlc4vghnnu7tnk5tekwm2kxn7e9rkrq7uslqmlu9sg6vl nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqs9lp9n8yjwjx56khduh7sqehtpgfs20d5w7x9lnjpnlt3vmqkpnmq7xfcef nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqsx4m8un5h952d6f7zuq9yraucs82lcah2p2lk4z6n9u0lduje2pcs40zhkz nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzq5pf4h2je6jkpypup9kj2k66qtlcmce3gcg9q39xpv5388u50sun6ku45d nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqkdwwjagam6rcxmakpcgsylu95zkm8s0qkvae8j2km6e5l5sr9alsm8vrfn nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqg9cqvgzvegmdsnc6xc5mhwnvsn9unyx4nx6megwcqxlheaddffc8ckpk3qj
16:00 - 18:30 山形駅でりらさん合流・産業科学館
車で山形駅まで戻り、りらさんと合流。
山形駅内の産業科学館を見て回りました。産業科学館は子供向けの知育ブースや山形県民向けの各種企業ブースもあり、見ていて飽きないものが沢山展示されていました。
発電機を回してミニカーを動かすゼネコンレーシングが楽しかった。
また、各種企業ブースを回りながら、Junさんに山形県民憧れの就職先などを聞いていました。産業科学館
http://y-sunka.org/
nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpx0ykjd6egvded9jksguphr4deluxlz56dm4rpw9n68npx9wt3hx976mcl nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpek5k3fygrx8y0024mmmnhqxdnd7jmqed7gf7sqt2tnushcv8xu7dwwctd nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyzzfwt63psqw4w5x7s33al0k0ms2v80p88vjjjd4rx7f8t4juppkux27ek7 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqgj58fqpvpngr2vafhdcqtf5vn264960dad73kqfrem3m27hr6mpstqgs5t nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyrnaxmkc47f5p46p36v8qnf4pr5ktm5algd86fsgzw9de96n9yp4qxu6dl8 nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypehj7clkzll3yf7yftcp5t9k6dfnetvrpl943q4jd8ccy39neq66nyavjs nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqnc3mmp8sg4lysfkcz7x4ft3c6rrulne8aetvd8lwkzz86k8fp9lt040df nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqgdms2ltla34u9qr4whzlz69r3mpsj7e3jlpv935yltn799xsk89d3a6g4
18:30 - 20:40 旅館チェックイン、夕食
私 / あめさん / りらさんで、喜三郎という温泉旅館に泊まりました。
ここの温泉の泉質は芒硝泉(リウマチ・高血圧・切り傷・婦人病に効くとのこと)で、保養温泉として親しまれているそうです。
夕食のしゃぶしゃぶ、サザエ、釜めし、芋煮、... 全部旨かった!!!
夕食を食べていたら意外と時間ギリギリになり、露天風呂は朝入ることにして爆速で風呂に入りました。温泉旅館 (喜三郎)
https://kisaburo.jp/
nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyqr9wgwca9jknh88c83nq3n5nnqtflrrd4v5d7uhuh9d47a2qsl870yprel nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyr6yt65e79gqh4dp8pll2kfgaw837xulq2jh2x3y9zd4udk47lkn55pqkzm nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqwdv2aa4n5z5r5k8q3z2retc9zgujytx9z36xmpsw6h9npc97250qkne529 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzp2rhy02kfw73jtzq7t7sp2njn2gnt9elta7nm09u55csld8kg5t39lh49r nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyzv32r03thal6tvjqh4wgxk6xv6x2tkuwngw6kfv6ar49rg2yq55jc8arsp nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqy2duq6xsl8jwns0r7qxgpf6703uwvawrhhlanytrepd082mnyugqxnxpj3
20:40 - 23:00 二次会
二次会の居酒屋でJunさん、Donさんと再度合流。
Junさんの奥さんで漫画家をされている、横谷先生も来てくれました。山形の地酒を飲みながら、Nostrasia 2024での思い出 / 山形の特産品 / Junさん夫妻が東京にくるタイミングはいつか など話していました。
横谷先生はM3やコミティアなど東京に来られるタイミングがいくつかありそうでしたが、Junさんが東京に来るタイミングはなかなか無さそう。
山形にまた会いにいくか、東京で面白いイベントをやって呼ぶしかない!また、山形には「ほや」と呼ばれる海産物が有名という話を聞きました。
ほや、結局食べ損ねてしまった。山形うまいものと地酒 母家
https://r.gnavi.co.jp/t846900/?sc_lid=smp_top_01
横谷先生の読み切り : 遠い日の陽
https://comic-days.com/episode/14079602755391426482
nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqgplnrvwhk6hsl9rk979u6qtmnmrpgywdgexruznhmtkmyevsaua8s8cy2pq nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpkwu2t5zgug7wlwqh8nfh4zyma3f6tlacx9dag4kawnq7nynkxr33rdgaz nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpq8szzc33567mtsjnvajzgur9n8us3fuv2ckx86y0et3c7kddqd37uxuz0
23:00 - 旅館に戻る・就寝
旅館まで車で送ってもらい、旅館で就寝。
翌日も朝早いので、恒例(?)の枕投げやトランプをして遊ぶこともなく、12時に消灯しました。10/13
6:00 - 起床・露天風呂 ~ 7:30 朝食 ~ 8:30 チェックアウト
前日に入れなかった露天風呂に入るため、早めに起きて露天風呂に入りました。
旅館の窓を開けると須川が流れていて、天然のASMRを感じられました。nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpz260lg35sg06h758y7eppvrwzypv5kc3yj4n0t8jyx5q4f82mse3ung9s nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqt6cyt5hmatsuct2plneae7t0apnkkrxm38hvee3auhu0h3hljjgs943h27 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzp2qq9lv0d3umyxprne6xpjj70af6flzcfs2qpgsx2r347q7ukpdm2rwml4 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqgaugf683lhlww8ynlgd7qfhgj2d3zlkecm72td35lfw6m4tkvhke4k8jt nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyz750rwdqdk0x8r08m96fcyf5l4wp9pmc0rz8mle02ygtrdzdhf0gjwc823 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqq36wgay36wz58kmjvsucple6whamvd28pqrhu082wsdkkpvxzht34tq02
8:30 - 移動・買い物 ~ 9:40 Junさんの家に移動・芋煮会開始
近隣のスーパーで芋煮会用の買い物を済ませたあと、Junさんの家に移動して芋煮会を始めました。 あめさんが帰宅の関係上、山形駅を11:11に出ねばならず、芋をよく煮るために爆速で芋煮を作る必要がありました。
皆で協力して爆速で芋煮を作り、しっかり煮えた状態の芋煮をあめさんに持って帰ってもらうことができました!nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqe03zqdcpjzakz3u7jjs07crz05y024lvgmjuvh0zysf4zal9q0la8772q nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpq6xaa2etzypq7hlm8zs3rkrjsc0wh5c29huupe9mfxqqeu5uanttq39l9w6 nostr:nevent1qqs0zkh2t2crsv8ljxzvmy3ndwzncyl6wwz67hfy4p09tacem3pjzwg2h4ac8 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpq3ugypvt2fw886375nzltef4fzlasvk7nzj5n9tpuunwrr4p9etasskzqd6 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpq9u5559ucupe755xnlm00vm5wcj7rpu3wwc3wvrdjxxdcadcwumzqjg8e6r
芋煮ビルド過程
nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypn3w96w3wu375rz5hwhwhnmvrc664dltaudzvt578s6dh6kzq205u0m44v nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypc0nxkt4ht0ku9l4hjmvtlv9rh5lt496r7s3755clg7q45fypnxkjms92t nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypdfx9umwcyupt4cx38klfhl0f3saf3ar47jr7rcyj69dzyxve7tqk8wmcm nostr:nevent1qqsve084cxu5kw3gvqhjaehfge202z2nyddft89ufn9j73wyynwzhwczwz8j2 nostr:nevent1qqs26rp3gc2dhz4yznynym0y3c6y257kt2u773dvaaf87uf40fzjmcqk2zxxm nostr:nevent1qqsf3jx69s6guydhfxqstcw2m5aaw0zpum74aawe79nhz3xyg7p7dks0x9gn5 nostr:nevent1qqswtgfxseqwnt424ay668ps782drdmxkyyqj8uk8lfxs264gayfnkg3ls82a nostr:nevent1qqsqd257ng55ynkrwe3v2skcx29xalz85qcgn3ghj8ug4lqt9ewqvwgshz303 nostr:nevent1qqsw04zd3wgd3c5ztave9yhhavupl7pc3e4rcke5qn4azn8gpctz23cm7e5p8 nostr:nevent1qqsv8kqnr36jyhj9tnc602p6njakhgcuf6klm0xfrsngjrxlej9068s9vz3jg nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyrpm5t3gxyjxnfw6y8eu2j0mpgf8acj83c86ueykdqke6nxchjku63rl6q5
11:20 - 14:30 Junさんの家でまったり・ねるねるねるね
Junさんにあめさんを駅に送ってもらった後は、残ったメンバーでテレビを見たり、ねるねるねるねを作って皆で食べたりしていました。
りらさんが仙台に行くため、14:30で帰っていきました。nostr:nevent1qqsya6u4r9amxs32m4k45s9203ph3kwmtlyddq283zrtyufk3z7tk9gaw3dyv nostr:nevent1qqs0nr6xznhxr4hfrczatlgy26lcrlup3zg8ey6j6ldthxnu9fy3mfq7tauam
14:30 - 16:30 伺かレクチャーを受ける
Junさんにりらさんを送ってもらっている途中、せっかく伺かベテランのDonさんがいるので
伺かを始めました。
※元々伺かやSSTPには興味があった
Donさんに伺かの基礎や「Nostr x 伺か」のOSSの機能などをレクチャーしてもらいながら、
Nostrと伺かで出来ることを話し合っていました。個人的に驚いたのは、一方通行で喋らせるだけだと思っていた伺かが、SSTPを通じてデスクトップマスコットとシーケンシャルに「やりとりができる」ことです。
非常に拡張性が高く、Nostrと同じで無限に遊べそうな雰囲気を感じました。伺か (うかがか) とは
2000年5月25日に初公開されたデスクトップ常駐型のフリーウェアで、24年間色んな人が発展・メンテナンスしています。
SSTP (Sakura Script Transfer Protocol) と呼ばれるプロトコルで指定のポート番号 (9801番)あてにメッセージを送ると、デスクトップマスコットを喋らせたり色んなことができます。
プロトコル仕様が公開されており、SSTPクライアントやサーバー、ベースウェアまで自作することが可能です。詳細 https://dic.nicovideo.jp/a/%E4%BC%BA%E3%81%8B
伺か参考 (ばぐとら研究所)
現在デファクトスタンダードとなっているベースウェア、SSPがここからダウンロードできます。 https://ssp.shillest.net/
nostr:nevent1qqsyrz64vff9fjkpj297qyr278d2a58l3fuysgknsm8jwyuwy6v8hcgvmn4mt nostr:nevent1qqsdzfjfvxxk5ph49x40s3hf8pdgazzq2x5xekd6ztqnqw4y4z3r8as4pdywy nostr:nevent1qqsr8sdds33g53asp7c45v3eems3vj3qhtxayvku9nxext95aauuuaq4d6t0x
16:30 - 17:30 四谷ラボの配信アーカイブを見る・帰宅
Nostrasia 2024やBluesky meetup、Nostr勉強会の配信アーカイブを見ながら、当時の思い出やNostrの未来について語っていました。
こういうのを忘年会や新年会でやっても面白いかもしれない。
18時の山形駅発の新幹線を取っていたので、18時にJunさんに駅まで送ってもらい、山形を去りました。四谷ラボの配信アーカイブ
https://www.youtube.com/@428-lab
終わりに
私は1泊2日でしたが、山形を味わい尽くしてリフレッシュすることが出来ました!
今回、Junさんには企画だけでなく車で色々連れて行ってもらったりと、本当にお世話になりました。
次に直接お会いしたら、何かしらもてなしたい。また、Donさんに直接会えて色々話せたのは本当に貴重でした。聞くところによると、Nostrのオフ会だけでなく、歴の長い伺か仲間とのオフ会も出たことがないらしいです。
また山形に行きたい!と思えるようなオフ会でした。
-
 @ 1eb966a6:e3eddf94
2024-11-09 13:18:54
@ 1eb966a6:e3eddf94
2024-11-09 13:18:54deleted
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-06 17:44:00
@ 5d4b6c8d:8a1c1ee3
2024-11-06 17:44:00Now that Trump is heading back the White House, once again promising to "drain the swamp", let's consider how that might actually be accomplished.
It's damn near impossible to fire federal employees and abolishing entire agencies is very difficult politically. The later hasn't been done since Jimmy Carter. Of course, I'm all for Ron Paul and Elon Musk pursuing both of those paths, but they'll definitely be ice skating uphill.
There are two proposals that I know will result in massive voluntary resignations, labor savings, and reduction in DC bureaucrats: 1. Relocate departments and agencies away from the major metropolitan areas 2. Rescind locality pay for remote eligible workers
The first option was implemented by Trump for a couple of agencies. It was big news in econ world when the USDA was relocated, because hundreds of USDA economists resigned.
I'm not sure how easy it would be to implement the second idea (perhaps @Cje95 can weigh in), but it would also have a dramatic effect. During the pandemic, the feds followed the trend of making many positions remote work eligible. However, the federal pay scale still grants locality based pay increases for those living in expensive areas. If you are allowed to do your job from anywhere, why should you get an enormous raise (at taxpayer expense) for living in the most expensive place in the country? Pay all remote eligible workers as though they live in rural Arkansas, because they are allowed to do so.
As with the relocation, most workers would probably resign rather than either move or take a huge paycut. And, if they don't, then at least the federal workforce is getting spread out and not costing nearly as much.
What are some other feasible ways to dramatically reduce the federal workforce?
originally posted at https://stacker.news/items/756327
-
 @ 1eb966a6:e3eddf94
2024-11-09 13:18:25
@ 1eb966a6:e3eddf94
2024-11-09 13:18:25deleted
-
 @ 9e69e420:d12360c2
2024-11-09 12:49:50
@ 9e69e420:d12360c2
2024-11-09 12:49:50The historic auction of Steve Lazarides' Banksy collection represents a significant moment in street art history, offering unprecedented insight into one of the world's most enigmatic artists. The collection, which sold for approximately $1.4 million at Julien's Auctions, featured over 170 lots of rare artworks and personal artifacts[5].

Notable Sales
The auction's centerpiece was an original proof print of "Girl with Balloon," embossed with the P.O.W. (Pictures on Walls) mark, which sold for $104,000, significantly exceeding its $60,000 estimate[5]. Other significant pieces included:
- A Banksy "Hooded Figure" painting that fetched $78,000[1]
- An original hand-cut stencil featuring Banksy's name, selling for $58,500[5]
- Original concept sketches for the "Paparazzi Rat" stencil series on a manila envelope, which achieved $52,000[5]

Personal Artifacts
Among the most intriguing items were 15 "burner" phones used for communication between Lazarides and Banksy[1]. The collection also included Banksy's worn Puma "Turf War" sneakers and various personal items that offered glimpses into their working relationship[8].
Historical Significance
The sale represents more than just a collection of artworks; it documents a pivotal period in street art history. Lazarides and Banksy established Pictures On Walls (P.O.W.) with the mission of creating affordable art for the masses[1]. As Lazarides noted, "For a very short moment in time we made a difference, we made it OK for ordinary people to like art"[8].
Legacy and Future

While Lazarides has retained some personal items, including angry notes from Banksy, he stated he doesn't need "1,000 prints to prove I worked with Banksy"[5]. This auction not only celebrates their collaborative history but also marks a significant transition as Lazarides returns to his photography practice[5].
The sale underscores the enduring value of Banksy's work and the continuing intrigue surrounding his anonymous identity, which has become central to his artistic brand[3]. It also highlights how anonymity in street art can paradoxically enhance an artist's fame and market value[9].
Sauce: 1. Banksy's Girl with Balloon print sells for £80,000 at auction
2. Who is Banksy? A guide to the street artist, printmaker and anti-establishment provocateur
4. Overview of Banksy Prints - Banksy Explained
5. Banksy's Right-Hand Man Cashes In, Selling His Trove of Work By the Street Artist
6 .Branding the Unbrandable: Banksy and the Mystery of the Anonymous Brand
7. Banksy APs | Guide | Andipa Editions
8. Historic Banksy Collection from Steve Lazarides to be Auctioned at Julien's
9. Unmasking the Mystery: The Role of Anonymity in Street Art and the Enigma of Banksy
10. Market Watch Banksy: Top 10 Most Investable Prints | MyArtBroker
11. JULIEN'S AUCTIONS ANNOUNCES "UNDER DURESS: THE BANKSY ARCHIVE OF STEVE LAZARIDES AUCTION"
-
 @ fca435eb:e53931d9
2024-11-06 17:38:35
@ fca435eb:e53931d9
2024-11-06 17:38:35Setting up a hybrid lightning node, even behid CGNAT:
1. Motivation
To run a lightning node in a completely sovereign way, we must host it on hardware under our control. To make our node accessible to other peers we must publish on the gossip network how to find our node, but since many of our local networks are behind a carrier grade NAT and the router does not have a public IP, it becomes a bit difficult. In this post I will explain how to expose our node with a ssh tunnel with a vps, even behind CGNAT. I won't explain how to create a tor hidden service because I think is trivial, if you are running a node, almost sure that you have one.
2. Prerequisities:
1- Running a lightning node 2- Having a vps with a public ip: lunanode is easy to use, and you can pay with lightning
3. Exposing the node
Connect to your VPS by ssh and edit /etc/ssh/sshd_config
sudo vim /etc/ssh/sshd_configEnsure that:AllowTcpForwarding yes GatewayPorts clientspecifiedMake sure that the port that you want to expose is accessible by the internet, in my case it will be the default port 9735, replace 9735 by your custom port if you want:sudo ufw allow 9735 sudo ufw reloadNow let's move to our local machine, where the node is running. With the assumption that your node is exposed in localhost:9735 (that's how it is by default) let's test our implementation, remember to change the ports if you have others, paste your vps public ip address and your vps user :ssh -nNTv -R 0.0.0.0:9735:localhost:9735 **YOUR_VPS_IP_ADDRESS**Now you must change the config of your node to advertise the new address. If you use CLN you can edit the config file and set announce-addr=YOUR_VPS_IP_ADDRESS:9735 (or your port). If you are using another lightning node implementation I am sure you can find the config file, and announce the address. Now everything must work, you can try to find your node from another node (maybe a friend's node) by the new ip:port address and the pubkey of course.4. Finishing
You can close that now, and prepare to make it more robust. First we need to install autossh
sudo apt-get update && sudo apt-get install autosshCreate system d service
sudo vim /etc/system/systemd/autossh-lightning.serviceand there put the service description, remember to replace the needed fields with your own data. ``` [Unit] Description=port forwarding through auto ssh After=network.target
[Service] User=USERLOCAL ExecStart=/usr/bin/autossh -M 0 -o ServerAliveInterval=30 -o ServerAliveCountMax=3 -i /home/USERLOCAL/.ssh/id_rsa -nNTv -R 0.0.0.0:9735:localhost:9735 YOUR_VPS_IP_ADDRESS
[Install] WantedBy=multi-user.target ```
Then run:
sudo systemctl start autossh-lightning sudo systemctl status autossh-lightningIf status is active we are all set.originally posted at https://stacker.news/items/756320
-
 @ 82b30d30:40c6c003
2024-10-11 12:25:34
@ 82b30d30:40c6c003
2024-10-11 12:25:34[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
[32]
[33]
[34]
[35]
[36]
[37]
[38]
[39]
[40]
[41]
[42]
[43]
[44]
[45]
[46]
[47]
[48]
[49]
[50]
[51]
[52]
[53]
[54]
[55]
[56]
[57]
[58]
[59]
[60]
[61]
[62]
[63]
[64]
[65]
[66]
-
 @ 82b30d30:40c6c003
2024-10-09 03:51:41
@ 82b30d30:40c6c003
2024-10-09 03:51:41[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
[32]
[33]
[34]
-
 @ 0861144c:e68a1caf
2024-11-06 16:20:18
@ 0861144c:e68a1caf
2024-11-06 16:20:18I saw many people here (and other sites) claiming that they voted Trump because he will pardon Ross Ulbritch. Politicians live from promises and is their biggest bond. Since Trump have the...experience of saying half-truth, one possibility is that he doesn't pardon Ross and still in jail.
As non-US, all I can do is zap my support to their legal fund. Trump doesn't release Ross, what is the next step?
originally posted at https://stacker.news/items/756208
-
 @ 7e6f9018:a6bbbce5
2024-11-09 12:12:41
@ 7e6f9018:a6bbbce5
2024-11-09 12:12:41Handshake is a decentralized, permissionless naming protocol where every peer is validating and in charge of managing the root DNS naming zone with the goal of creating an alternative to existing Certificate Authorities and naming systems.
Names on the internet (top level domains, social networking handles, etc.) ultimately rely upon centralized actors with full control over a system which are relied upon to be honest, as they are vulnerable to hacking, censorship, and corruption.
Handshake aims to experiment with new ways the internet can be more secure, resilient, and socially useful with a peer-to-peer system validated by the network's participants. By running Handshake, one can participate in a decentralized open naming platform secured by a decentralized peer-to-peer network.
https://github.com/handshake-org https://github.com/imperviousinc/fingertip https://handshake.org/
-
 @ b4403b24:83542d4e
2024-11-06 13:43:13
@ b4403b24:83542d4e
2024-11-06 13:43:13originally posted at https://stacker.news/items/755988
-
 @ 319ad3e7:cc01d50a
2024-10-08 14:33:14
@ 319ad3e7:cc01d50a
2024-10-08 14:33:14https://image.nostr.build/4824c65d9a07c577bee8591b18ee147e7a457849fbaee53244667ec062914751.jpg
OCT 2024 | ISSUE 2 | LETTER FROM THE FOUNDER | LIFE EXPERIENCE | FEATURED RECIPES | REVIEWED RECIPES | ECONOMICS | MICROFICTION | FAMILY FOODLOVE | FOOD SWOON | NOTE SYNCING | SOUNDS | QUOTE OF THE MONTH | UPCOMING EVENTS | ANNOUNCEMENTS | LANGUAGE | #NOSTRASIA2024 ALBUM | FINAL THOUGHTS
LETTER FROM THE FOUNDER 📝
Hey Everyone!
Exciting things are cooking at Zap Cooking! We’re thrilled to announce that we’ll be in Happy Valley, State College, PA, on October 12th as proud sponsors of Nostr Valley. It’s shaping up to be an incredible weekend, and we can’t wait to share it with you! We’ll be hosting a dynamic panel that dives deep into the intersection of food, culture, and, of course, the unique world of Nostr. This event promises a great mix of good times and engagement, and we’d love to have you join us! If you're interested, sign up now at nostrvalley.com.
We’re also excited to have you reading our second monthly newsletter. At Zap Cooking, our focus goes beyond development - we're committed to creating content that inspires. Follow our npub on Nostr to catch flavorful food ideas and captivating creative content. We’re working on fresh perspectives and new projects that celebrate cultural diversity, all while keeping the quirky, authentic spirit of Nostr alive. Thanks for being part of this journey with us. Let’s keep Nostr weird and delicious!
Seth
https://i.nostr.build/nQqsPGmJ8hjvxROK.png
Artwork by Bread and Toast | https://breadandtoast.com/
LIFE EXPERIENCE 😮💨
In August 2024, Nostriga held the afterparties at the Basement, an underground Bitcoin bar in Riga, Latvia. The crowd spent the nights enchanted in conversations, dancing, drinking, and smoking cigars to celebrate freedom and life.
It was a fascinating experience smoking cigars with the Nostr men on those cobblestone streets, reminding me of my younger years working in a private social club, where the cocktail lounge would fill with a thick layer of cigar smoke as I crafted and served Bourbon or Rye Manhattans, Old Fashioned cocktails (one with Sweet 'n Low!), and neat single malt Scotch whiskies.
Recently one of the voices of Nostr - The Beave - tagged me in a note, introducing me to Duchess and their love of coffee & cigars. In less than twenty minutes, Duchess and I were collaborating for the next Zap.Cooking newsletter. The following review is going to take us out of the nightlife and into a morning zen session. - SimplySarah
CIGAR & COFFEE | Duchess
https://image.nostr.build/eff42693d5d4c9f086c25a11e57563b5163dad2f3da600de5e835ba2e1a1a842.jpg
There’s nothing quite like starting your day with a good cigar and a cup of coffee. The rich, earthy flavors of a cigar paired with the bold aroma of coffee create a perfect harmony that awakens all the senses. The Coffee will give you that little morning boost, while the cigar will ease you into a calm, zen-like state. Together, it’s a ‘boosted zen’ that really sets the tone for a productive yet relaxed day.
CIGAR | PDR 1878 DARK ROAST CAFE
A cigar known for its rich, coffee-infused flavor. This particular one is designed to complement a dark roast coffee experience.
https://image.nostr.build/0ab1bb066281c4d6ed2cf0f65548076255535552c27b7a723953bd1ba5713cbe.png
The PDR 1878 Dark Roast Cafe cigar has a unique, slightly spicy profile that pairs beautifully with a cup of dark roast coffee. The coffee I paired with my cigar this morning was one of my favorite dark roasts: Jamaican Blue Mountain Roast, from Jamaica. Another dark roast that I love but didn’t have on hand is Black Ivory Coffee from Thailand.
COFFEE | JAMAICAN BLUE MOUNTAIN COFFEE
Known for its exceptional smoothness, mild flavor, and low acidity, Jamaican Blue Mountain Coffee is one of the world’s most luxurious and sought-after coffees. Grown at high elevations in Jamaica’s Blue Mountains, this coffee is loved for its balanced and refined taste.
https://image.nostr.build/57700f4defe71f9f01c9406ca7c1d6cbf4ccdc621a9b48db31065834079b0b17.png
Most purists drink Jamaican Blue Mountain Coffee without milk or cream to fully appreciate its unique and subtle flavors. However, I like to add fresh cream from the farm if you have access to a local farmer. I feel that adding cream creates a richer, smoother cup, no matter what coffee I’m drinking.
Coffee and cigars are both fascinating rabbit holes, much like wine, if you're interested in going down them.
ENJOYABLE PART OF SMOKING A CIGAR | Cigars are enjoyed primarily for their flavor. The rich taste of a cigar comes from the blend of different tobaccos, which is best experienced by holding the smoke in your mouth, where your taste buds can fully appreciate it. Inhaling isn't necessary and actually makes the experience less enjoyable because cigar smoke is much stronger and can be harsh on your lungs.
HEALTH BENEFITS OF SMOKING A CIGAR | Nicotine, in small doses, can have some positive effects, like improving focus and mental sharpness. It also stimulates certain receptors in the brain that can support heart health. Cigars are the healthiest vehicle to deliver nicotine into your body, as they offer a slower, more natural release of nicotine compared to cigarettes or other forms of tobacco.
ENJOYABLE PART OF DRINKING COFFEE | Coffee is widely enjoyed for its flavor and aroma. The rich, complex taste of coffee comes from carefully roasted beans, which can range from bold and dark to mild and fruity, depending on the origin and roast. Sipping coffee slowly allows the palate to savor the intricate layers of flavor, from chocolaty and nutty to floral and fruity notes. Whether black or with milk, coffee offers a comforting and energizing experience.
HEALTH BENEFITS OF DRINKING COFFEE | In moderate amounts, coffee offers several health benefits. It is rich in antioxidants, which are known to support heart health, brain function, and help combat inflammation. The caffeine in coffee can boost focus, mental sharpness, and physical endurance by stimulating the central nervous system. Some studies have also suggested that coffee may support heart health, improve metabolic rate, and reduce the risk of certain diseases, such as Parkinson’s and Alzheimer's. Organic coffee—free from pesticides and chemicals—provides a cleaner, more natural source of these benefits.
Find Duchess on Nostr: duchess@orangepiller.org
FEATURED RECIPES 🥪
https://image.nostr.build/8ec8e09bc081e7f70de446fda8fc85d485c01ed4579b13f511753568b21f3c8b.jpg
https://image.nostr.build/e902abea3014325e848f7cbc8f1bd00f8899880fedcd2490361d12ec595c451a.png zap.cooking/recipe/naddr1qqsxxmrpwdekjcedwp3zv63dwa5hg6pdvykkx6r9v4ehjtt5wa5hxaqzyzmjwnfgu05c80mjpk6tfgf2x86u0mexyvsdqhp9ajgy3xkfjc5vkqcyqqq823cfuzkwc
https://image.nostr.build/b2a84afc5ea7948c3f8087b555ce9a43a5f543402b1ecb283cc884b93f1f8a2b.png
zap.cooking/recipe/naddr1qqvxyet9vckkzmny94sh2cn9wfnkjmn9943h2unj0ypzq3xurskmnslm67lwjft7e66jhc7033qt4aak8arw266c5ycuwnctqvzqqqr4guhg7y8e
https://image.nostr.build/ec7ef7667e252d63164682ed420ae94dc15758798cd80d62e8491ec35cef0f69.png
zap.cooking/recipe/naddr1qqfkvetjd4jkuar9vskksmm5945x7mn90ypzqqwsh0u4xlh3l5xalq2lg8qcjeec7636pasq75w8s2ma3zg3xr2vqvzqqqr4guvhlwd6
https://image.nostr.build/13b8af46a09dcf0ab04a37aae7f22c16fe31740ef4bc0984e8cf7b582e45332f.png zap.cooking/recipe/naddr1qq8xyetpdeej6mmw946x7ctnwspzp89qh469qapddgsrr8qw84xx08y7q34fm3cw3m64c2g9ufq9ydqtqvzqqqr4gug3lkp4
RECIPE REVIEWS ✏️
https://image.nostr.build/5ef1e884bde50d01215de6c3ed63e2d9a78bac0bd8eade1df6bf91c1b63ad3c1.png zap.cooking/recipe/naddr1qqtkwctjd35kxumpw43k2ttxdaez6ctw0ykkycn3qgswat02dja4qx9pjrcpz7zhmegnesn36fxfgl2kekpv2jntvjhy0fqrqsqqqa28m4rxcx
https://image.nostr.build/96299dcb152c513360f171038d032de102c29497634e1ba7b60abc1b215a4a42.png zap.cooking/recipe/naddr1qqjkket5dukksctd9skk2em895nz6cmgv4jhxefdvfex2cttveshxapdvd6hquczyzdu956dmk5rm9p2rlwndf6g07d2a36qmvjw57tn9kgw8q73n555sqcyqqq823c8r4tsp
ECONOMICS 🍞
AN ARTICLE ABOUT BAKERS | Silberengel (4 minute read)
https://image.nostr.build/4f11eea6d6a5f7476c0bbe0504f57e7111454c9b30ee0816ee0f85816d240e3b.jpg
Let's Talk About Baking Bread
I've mentioned a few times, how large-scale central planning inevitably leads to artificial scarcity and rising prices. Allow me to illustrate -- using a completely invented allegory about bread -- that has absolutely no parallels to any economy you may already be familiar with…
Read More | habla.news/a/naddr1qvzqqqr4gupzplfq3m5v3u5r0q9f255fdeyz8nyac6lagssx8zy4wugxjs8ajf7pqqxnzdejxucnwvfnxvmnsd3cgqxylq
MICROFICTION 📖
GOOD DEEDS | Rustypuppy
Being a trail guide at the UCP (Unique Creatures Preserve) meant I saw a lot of weird things. Some I show to the tourists; some I don’t.
The starved, green-skinned toddler with the turtle shell back, beak, and dish of water on his head was one of the latter. As he ignored the bologna sandwich and devoured the cucumber salad from my lunch, I flipped through my identification guide. Finally found him in the Japanese yokai section; a kappa - known for drowning animals and people, loves cucumbers and sumo wrestling, can be friendly and helpful, empty the dish on its head to severely weaken.
I filled up his dish from my water bottle, and he followed me down the mountain trail. As soon as he saw the glimmer of water, he ran ahead and dove in. I assumed from the lack of frothing water and the fact he didn’t end up punted onto the bank meant the lake god had accepted him.
Later that week, two teens stumbled into our office. One guy, obviously stoned, wanted us to give him the official wizard certificate since he had just walked on water. The other guy, obviously drunk, said his friend needed the druid certificate because he had summoned a turtle to appear under his feet, which is how he had spent the past half hour walking across the lake. I told the intern to take their contact info and arrange a taxi.
The next day, I left a large container of cucumber salad at the edge of the lake.
RECIPE REFERENCE | Grandma’s cucumber recipe zap.cooking/recipe/naddr1qq0kwunpdejx6cf8wvkkxun9v9khjttrw43h2mtzv4ez6umpd3skgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxpqqqp65wss0rqd
Follow Rustypuppy | https://rustypuppy.npub.pro/
FAMILY FOODLOVE 🐤
https://image.nostr.build/c5b498d176a03742a864de6ae1c833107089e798e4a9c3c111b5be8850df2397.png
https://image.nostr.build/55a8948263766f0f4360d9bddb30ada915cae51a93b3d7be1b4a7a9e6cc21b71.png
https://image.nostr.build/f17a5dd1cf93ae0d20b7904e0e0274d4dda3a6dd4c90c506b512232af08bec83.png
https://image.nostr.build/ef81f242c481e60cff9dd4a66ac74326a8e27ff0f87ae1f51a915046eecb8258.png
FOOD SWOON 💌
https://image.nostr.build/a0eeb835a8eee1221f4e6aeeb884b5897eea7335680f2e5b35bee35b517db432.png https://image.nostr.build/f2a8a21cd1587a39d0ce5fe09ef5176b773416d0419a6b5fb404c02fa6616730.png https://image.nostr.build/c4f54698566500ace19d12bef5168b0a6e7047a0c8c1daa3faa207253177b104.png https://image.nostr.build/22a0aaacbf37e88db702db655a4f9e7b0692d586304e9ecfffa694f379a88fd9.jpg https://image.nostr.build/f3918b3c68dc04bc3aae4e5202702875ebd4668676abe64fbc1e8cb001dde3c2.png
NOTE SYNCING 🗒️
“..everyone needs to eat pizza. Each individual country can choose what toppings they want on their pizza, so whether that’s pepperoni or mushrooms or anchovies if you are weird…” | OpnState on https://fountain.fm/episode/dg7rlmtOICVDGwtr7Jnc
"I eat sardines out of the tin with chopsticks." | @the_beave
“Chef has renamed Sardines to ‘Salt Daddies’. Please inform the staff.” | @enki
“My segue into sardines #FoodPorn” | @Deva Pyne (talking about HowToFoodPrep’s Sardine Dish) https://image.nostr.build/0f979d1bb7c0ba3c600694b83c5bc8e84ce4ff039839fb9f9af7ea727accef8b.jpg
SOUNDS 🔊
MUSIC
MAN LIKE KWEKS x BILLIV
Shoutout to Man Like Kweks x Billiv for making songs about PB & J cool! | singing Go together like peanut butter and jelly... | NOSTR CITY | KWEKS x BILLIV • Man Like Kweks (wavlake.com) | https://wavlake.com/track/f46d82f2-7f26-4357-9258-32da68324f74 | Man Like Kweks made a special appearance on Detox Radio | https://fountain.fm/episode/hGH0AgRj6hvrZEnSlX6n/ | https://image.nostr.build/baf111d653e75e88fc818529ba7872563e72be9540b21d0dea70b712d565dadd.png
PODCASTS
PLEBCHAIN RADIO
https://image.nostr.build/748c4c9f104582f583c3e3e30603be3964d0ddd3c8041a72680d5b8d48bc7108.png Zap.Cooking's very own Seth joins former Nostr CEO Derek Ross on Plebchain Radio hosted by the infamous duo: QW & Avi | CLIP - Super Rare Nostr.Cooking Magnet | "That's one of those physical NFTs" | https://fountain.fm/clip/dTzOg3VXOtLaXdR28oKE
ON THE FLY WITH STU
https://image.nostr.build/56ac7daf7d8158cde5f31ac2555f03ba26fe9de1afb5eeb26f4ba54f350bb7b8.jpg Recommended listening from our new fly fishing aficionado, onthefly@iris.to with Stu aka ON THE FLY WITH STU | https://fountain.fm/clip/9KjsUBPwmnmpR11UscKP
THE BITCOIN PODCAST
https://image.nostr.build/53fcc6f8468f3f18d0920fa0dcf386c01b7f02833101984bb26fff31916da498.jpg A VERY special thanks to Walker, the host of The Bitcoin Podcast, for giving Zap.Cooking a shoutout on his platform | "Okay this is pretty neat. Recipes on Nostr. Like the recipe? #zap it. Check out https://zap.cooking #grownostr" | Please check out one of the best voices that Nostr has to offer at bitcoinpodcast.net/podcast
QUOTE OF THE MONTH 📣
"Nostr and Bitcoin will change the world because they're like peanut butter and jelly - decentralized freedom meets unstoppable money, making sure no middleman gets a slice of your sandwich!" | Uncle Rockstar✊
UPCOMING EVENTS 🥳
Submit your Nostr event with @ZapCooking on Nostr
Nostr Valley @ Happy Valley Brewing Company | October 12, 2024 - 12pm to 4pm (est) Sign Up @ www.nostrvalley.com
Nostrville 2.0 No Panels, All Party! @ Bitcoin Park | November 6, 2024 - 4:30pm to 7:30pm (cst) https://www.meetup.com/bitcoinpark/events/303283108/
https://image.nostr.build/d484fb5058f39d7f15dfe048dc91b1b697c45c117612ec0202d8a5bb681af02a.jpg
ANNOUNCEMENT 📰
RABBIT HOLE RECAP REBRANDING
https://image.nostr.build/dacfbb06c6b76582814ad035ff44d9a66a885cdb97783e56b491d6b2e4b6d1f5.png https://video.nostr.build/a6b670ea0839d2d5d35ee4d38d9a082a0ce4b93aeb6ffaad18c89de829ccbc95.mp4
https://rhr.tv/ | Please send them a warm congratulations! 🤠
https://image.nostr.build/497029805a46bbb4942bcb13a0e8f0238e3c7956282d4d2866ca342d19f54bad.jpg
LANGUAGE 🏫
SCHOOL'S IN SESSION
Write "egg" in 50 of the Most Popular Languages
English: egg | Spanish: huevo | French: œuf | German: Ei | Italian: uovo | Portuguese: ovo | Russian: яйцо (yaytso) | Chinese (Simplified): 蛋 (dàn) | Japanese: 卵 (tamago) | Korean: 계란 (gyeran) | Arabic: بيضة (bayda) | Hindi: अंडा (anda) | Bengali: ডিম (dim) | Turkish: yumurta | Vietnamese: trứng | Thai: ไข่ (khai) | Persian (Farsi): تخممرغ (tokhm morgh) | Swedish: ägg | Danish: æg | Norwegian: egg | Finnish: muna | Hungarian: tojás | Czech: vejce | Slovak: vajce | Romanian: ou | Bulgarian: яйце (yaytse) | Ukrainian: яйце (yaytse) | Malay: telur | Indonesian: telur | Filipino: itlog | Swahili: yai | Serbian: јаје (jaje) | Croatian: jaje | Bosnian: jaje | Lithuanian: kiaušinis | Latvian: ola | Estonian: muna | Icelandic: egg | Maltese: bajda | Welsh: wy | Irish: ubh | Scottish Gaelic: ugh | Basque: arrautza | Catalan: ou | Galician: ovo | Armenian: ձու (dzu) | Georgian: კვერცხი (k'verts'khi) | Tatar: йомырка (yomyrka) | Kazakh: жұмыртқа (jumyrtqa) | Tamil: முட்டை (muttai)
#NOSTRASIA2024 ALBUM 📷
https://image.nostr.build/9243af94d1ae162bcf9ea14baad39286c4162dc838dd3d82f988e7a032f50328.png
Community Photos & Videos by A.k.A. radish on fire🎤 @hakkadaikon, @HonokaShisha, @Kojira, @Jeroen and the contributors of the hashtag #NostrAsia2024 | Share your Nostr community photos or videos with @ZapCooking
MESSAGE from A.k.A. radish on fire🎤 @hakkadaikon
Hello!
Thank you very much for coming to Nostrasia 2024 on the 23rd of September!
Now, you can see the live-streamed videos of the speaker events and the afterparty from the YouTube archive. Please check them out especially if you could not join the talking events. You can jump into a session you like from the chapter lists in the video descriptions.
Thank you!
Nostrasia 2024 Part 1 https://www.youtube.com/live/i-oHjdYWo1E
Nostrasia 2024 Part 2 https://www.youtube.com/live/tGeHKrqTA4A
Nostrasia 2024 Part 3 - Afterparty (Tuna cutting show) https://www.youtube.com/live/ery0aWATjWk
GIKOGIKO KAIJI TUNA | KOJIRA
https://i.nostr.build/Y2jTdGxblC98KeWI.jpg https://v.nostr.build/dKSZbmNOZ9JbM8wv.mp4
SHISHA CAFE, BAR & COMMUNITY SPACE
https://i.nostr.build/UdNbeXdB628wW2dK.jpg
JEROEN'S TOKYO VISIT
https://image.nostr.build/8e384c2620088f3fe5001f797576625649e0c0f53f3415193d2f51a92d16ba3b.jpg https://image.nostr.build/b43988efa086653155b7c9109ca5f4d2903adb5e0879a302a9ef743c05263523.jpg https://image.nostr.build/f2b584e728f95b747a5795741451df63c36c5eafef5886ecd3635c381bcd40e2.jpg https://image.nostr.build/d9e6c2ccd290a558202747e471ec5df025e0c37720f0563a7f5928ed56429a9b.jpg https://image.nostr.build/c9f5ec9f7ec03cd2f4d9c12f151e7548879b022590d063dc2226f5deb00c40f1.jpg https://image.nostr.build/cd58ed78004f46a65b84ea279fee5a07e4ca6762b4964b1b95149dde2303bc6a.jpg https://image.nostr.build/674ef0111ee987967bf1f98bb880bc3d7c4667033d5f067668881fd3d8bf1918.jpg https://image.nostr.build/5df690358d06cc62fe9260311d606c812a67a0d4b4b6779a3c48f4986446799e.jpg https://image.nostr.build/837696634b1e546ee1f6e2ec8cd1aa4f813df017010c4434c9b93291fa4a6d1c.jpg https://image.nostr.build/771c0b2f8e15aa901f4ef1da34be8843eeac716a1f792be714745283be71eecd.jpg https://image.nostr.build/48555bd4db7bb7f707dd78882dafd669cb1f860d851389d18ab0b1f2e3423da6.jpg https://image.nostr.build/76d3c990cb337d9f8a413032a0c4b7ab60c7b3faffc52baed6c7bcda9ddec8ee.jpg https://image.nostr.build/4c532360c28aaceb7fadbcc0ff0e9737be27d41a8213c79cbd0621f2b367a15b.jpg
FINAL THOUGHTS 🤔
What are your thoughts on the instant translation of food videos to enhance global accessibility?
https://video.nostr.build/4dba5f5e87d2f9bfda5f04dae82c3ce8d7cee41f19033906c6d59a60dd42a9a5.mp4
What is your opinion regarding Trump’s visit to PUBKEY and purchasing food & beverages with Bitcoin?
PUBKEY: * Smash Burger: $12.50 x 50 = $625.00 * Diet Coke: $3.00 x 50 = $150.00 * Subtotal: $775.00 * Tax: $68.77 * 20% gratuity: $155.00 * Total: $998.77 A former president spending #bitcoin at your bar: PRICELESS.
https://image.nostr.build/70c72f924b9cd8d429e0f1c030ce35c52604485e553f1c24af0b1d1737f3adc9.jpg https://image.nostr.build/f1bd17df540bceb7f8f4f2ed7979cc20c86e7d38ddc35d1d8988321c08cc1ee4.jpg https://media.primal.net/uploads/2/ed/89/2ed896f3be4eaec166230e582e4228a53d82652e38a90620aef09cb5da5b1c7d.png https://v.nostr.build/sbPbqOIvSpCffo4I.mp4
fin💐
September Issue 1 | https://habla.news/u/zap.cooking/ZAP-COOKING-NEWSLETTER-4yxs6s
-
 @ b4403b24:83542d4e
2024-11-06 12:05:17
@ b4403b24:83542d4e
2024-11-06 12:05:17Republicans are hilarious 😂
originally posted at https://stacker.news/items/755844
-
 @ 74718b83:b8204bd8
2024-11-06 11:09:14
@ 74718b83:b8204bd8
2024-11-06 11:09:14curious to hear some opinions on this as i know many hate the idea of the gov having anything to do with btc, on the flip side, having it as a reserve currency in a large country could be the thing that tips mass adoption and understanding on a global scale , which would mean more people waking up to the power of btc. it would also end the paper arguments no coiners make and silence them forever
originally posted at https://stacker.news/items/755779
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ 5f010feb:3ae9756b
2024-10-03 13:28:13
@ 5f010feb:3ae9756b
2024-10-03 13:28:13[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
[32]
[33]
[34]
[35]
[36]
[37]
[38]
[39]
[40]
[41]
[42]
[43]
[44]
[45]
[46]
[47]
[48]
[49]
[50]
[51]
[52]
[53]
[54]
[55]
[56]
[57]
[58]
[59]
[60]
[61]
[62]
[63]
[64]
[65]
[66]
[67]
[68]
[69]
[70]
[71]
[72]
[73]
[74]
[75]
[76]
[77]
[78]
[79]
[80]
[81]
[82]
[83]
[84]
[85]
[86]
[87]
[88]
[89]
[90]
[91]
[92]
[93]
[94]
[95]
[96]
[97]
[98]
[99]
[100]
[101]
[102]
[103]
[104]
[105]
[106]
[107]
[108]
[109]
[110]
[111]
[112]
[113]
[114]
[115]
[116]
[117]
[118]
[119]
[120]
[121]
[122]
[123]
[124]
[125]
[126]
[127]
[128]
[129]
[130]
[131]
[132]
[133]
[134]
[135]
[136]
[137]
[138]
[139]
[140]
[141]
[142]
[143]
[144]
[145]
[146]
[147]
[148]
[149]
[150]
[151]
[152]
[153]
[154]
[155]
[156]
[157]
[158]
[159]
[160]
[161]
[162]
[163]
[164]
[165]
[166]
[167]
[168]
[169]
[170]
[171]
[172]
[173]
[174]
[175]
[176]
[177]
[178]
[179]
[180]
[181]
[182]
[183]
[184]
-
 @ 000002de:c05780a7
2024-11-06 03:24:27
@ 000002de:c05780a7
2024-11-06 03:24:27You may not realize it, but you voted today. You vote everyday. Not in an election but in a much more mundane but infinitely more important way.
You voted with your time, talent, and treasure.
- What you gave your time to.
- What you gave your talents to push forward.
- What you spent your life force (money, savings, bitcoin) towards.
Its easy to let the world around you shift your focus. Make you feel good or bad for your participation in its rituals. But ask yourself.
What am I spending my time, talent, and treasure towards? Does it align with what I tell myself is important? Is it moving me and those around me closer to the world as I'd like to see it?
We have more control over our lives than any clowns that suck up to us for votes will ever have. Don't sell yourself short. You can become better. You can enrich others lives. You have value and worth. I believe our creator loves us more than we can even imagine. But, even if you don't believe that you can make your world better.
Make your vote count.
originally posted at https://stacker.news/items/755525
-
 @ fd208ee8:0fd927c1
2024-10-20 18:19:48
@ fd208ee8:0fd927c1
2024-10-20 18:19:48(Please note that this is not official financial or business advice, but rather a description of something we have done, on an informal basis.)
A long, long time ago
It's been nearly a year, since nostr:nprofile1qydhwumn8ghj7argv4nx7un9wd6zumn0wd68yvfwvdhk6tcpypmhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjj7qpqs3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqv5atj2 came into being, mostly as a lark, involving a couple of members of our private chat group. Our initial plan was to work toward bounties, but Nostr bounties are a bit of a biased, uncertain thing, and our enthusiasm for that quickly waned.
So, what to do? Here we are, we three (nostr:npub1ecdlntvjzexlyfale2egzvvncc8tgqsaxkl5hw7xlgjv2cxs705s9qs735, nostr:npub1wqfzz2p880wq0tumuae9lfwyhs8uz35xd0kr34zrvrwyh3kvrzuskcqsyn, and I): IT professionals with little time, but plenty of intellectual energy, a Slack chat, a GitHub repo, and lots of frustration with the Nostr status quo.
We were, you see, Nostr end-users. We loved the idea of the protocol, but we were being regularly stymied by the poor quality of many implementations.
- Why can I not login? Oh, they fixed the login! Nope, still can't login.
- If I press this button, it says it sent, but it didn't send. Where note?
- They announced a new feature, but I tried it and it didn't work. Oh well.
- I noticed a bug in the client, reported it, and the issue is just rotting away in the project repo. Ignored.
- The website/relay/repo was here... yesterday. Today it has disappeared, and taken my zaps with it.
It was enough to make us want to tear our hair out. We decided that what Nostr needed... what it really needed... was a Nostr Stable Version. Nothing glamorous. Nothing exotic. Nothing busy or excitable. Just something that stayed where you initially found it, ran, and actually worked. Something where you could report a bug and receive a prompt response. Maybe even something, where you could pay a reasonable fee and be allowed to have expectations of some particular service being returned. And who better to build such a version, than people who want to use it, themselves?
Things working is an underrated concept
I know that the very idea of software running as expected and websites not appearing and disappearing suddenly, based upon what some particular developer had for lunch, tends to be met with little but scorn, from hardened, seasoned Nostriches (who are convinced that bugs are all features), but I think the majority of potential users would see it differently.
I'm with the majority, on this one.
I like to click "save" buttons and have them save. If I publish something, I want it to appear under my list of published somethings. I like to type in the website address I always type in, and have it magically appear on my screen, as if there were a little man sitting at controls in my laptop, just waiting for me to write H-T-T-P-S... and then jump to attention.
My unreasonable expectations have no bounds, it is true. But unreasonable people are also people, so we would also like to have our own unreasonable things to play with. Scorn away. My save button will save, and my published something will publish, and my website will load every damn time, just to spite you.
In the larger scheme of things, you see, we win even if we fail, if we at least increase the competition enough, that things working becomes the new standard. We can simply prove, definitively, that it is possible for Nostr things to work, if they are built by people who care if they work. If we also have fun together, learn something new, and come up with some cool, novel use cases, then that's pure profit.
We can only win, at this endeavor.
Where to start?
Name that brand
So, we had a team, we had a business idea, and we had a heck of a lot of motivation. What we didn't have, is a name. (Never underestimate the importance of naming things.)
We decided to name ourselves "GitCitadel" because "git" sounds techy, hints at our GitRepublic project, and is reminiscent of open-source development, and "citadel" reminds us of Bitcoin. The republic is at home in the citadel, naturally. All other products also live in the same citadel, hence the naming-convention of prefacing everything with "GC" (i.e. "GC Alexandria", "GC Sybil", "GC Aedile", etc.).
Brand yourself
The next thing we did, was rent a domain and run a webserver on it. This is an important step because it gives you an Internet presence, allows you to have company NIP-05 and email addresses (a form of promotion), and it's simply exciting to have one. Feels so much more "official" and it helps increase the name-recognition of your company.
Define yourself
We then sat down, together, over the Internet, and figured out who we are. Not who we individually are, but who we are, as a company. A company, after all, (according to the Cambridge Dictionary) is "an organization that produces or sells goods or services in order to make a profit". Now, a company's profits don't have to be monetary, but they should be something tangible. A company, in other words, is a team of people working toward some defined goal.
What is our goal? Well, we decided to think it over, sat down with the newer additions to the company (you can see who they are, on our project wiki page, and came up with a Vision and a Mission:
The vision is what the overall goals of the company are, whereas the mission describes how those goals shall be achieved. Now, this is a sort of lofty, abstract statement, so it was important that we posted it someplace publicly (to keep ourselves accountable) and look at it regularly, so that we can ponder it and realign whatever we are currently working on, with this statement. We know the statement is well-designed, if considering it helps us make decisions about what to do next.
Pay yourselves
(I'm going to switch from "we" to "you", here, as it's easier to write this part, but let's just pretend I didn't.)
The next thing on the list, is to arrange the finances, usually by setting up a Geyserfund, with an associated wallet, and then deciding how the funds from the wallet will be dispersed or stored. (I won't tell you how we are handling that, as that's internal company business, but I'm sure you'll think of something clever, yourselves. Or just google it.)
I would encourage you to arrange to pay yourselves profits. Not merely because your idea is going to make you all fabulously wealthy and internationally famous (although, that is obviously true), but because profits are the most pure form of communication that consumers in the market have with its producers, and one of the best ways to make decisions and measure increases in efficiency (increasing profits and/or output, while keeping prices steady or falling).
Cutting off this signal, in order to look pious to outsiders, is to shoot yourself in your free-market foot. Nobody says that you have to spend your profits on the proverbial lambo and a bimbo. You could donate them to charity, reinvest them, or store them for your nephews to inherit, but pay them out, you should. You don't have to love money, to value it as a tool and use it shrewdly. Money is a measure, and companies should regularly measure themselves: against their previous state, against their potential state, and against their competition.
(Also, you can use money to buy a lambo and a bimbo, but you didn't hear that from me.)
Organize yourselves
Once you've been working together, for a while, you'll find that you need to figure out how to organize yourselves. The first step is to...
Form a board of directors.
Stop laughing. I'm serious.
Any company has at least two roles (President and Secretary), ideally held by two different people, so any single-proprietor company is a man down. Find a different person, to be your Second, even if they're just your confident, who lets you cry on your shoulder on The Bad Days, when your code refuses to compile, and can tell people that you've become a Bitcoin millionaire and have gone on a sabbatical to hike the Himalayas and will be back in 3 months on The Very Good Days. Because business man was not meant to be alone.
If, like us, you're a small herd of people and have already been working together for a while, then this step is actually really, really fun. Just think about what people are already doing, and put a label on it. That role is now defined and it is clear who is in charge of what.
Scientists become "Chief Science Officer" or "Scientific Advisor". The person who always writes the okay, so this is what we've decided comment in the thread becomes the Secretary, the one managing the Lightning wallet and worrying over paying for the servers is the CFO, the person running the remote server becomes the CTO, and so on and etc.
And everyone knows who the CEO is. Everyone always knows. They do. Just write it down.
Agree how to disagree
Now, have the secretary write up a Member's Agreement. It's a contract between the members, about whatever the group thinks is important concerning the way the company will operate. According to Investopedia, common topics are:
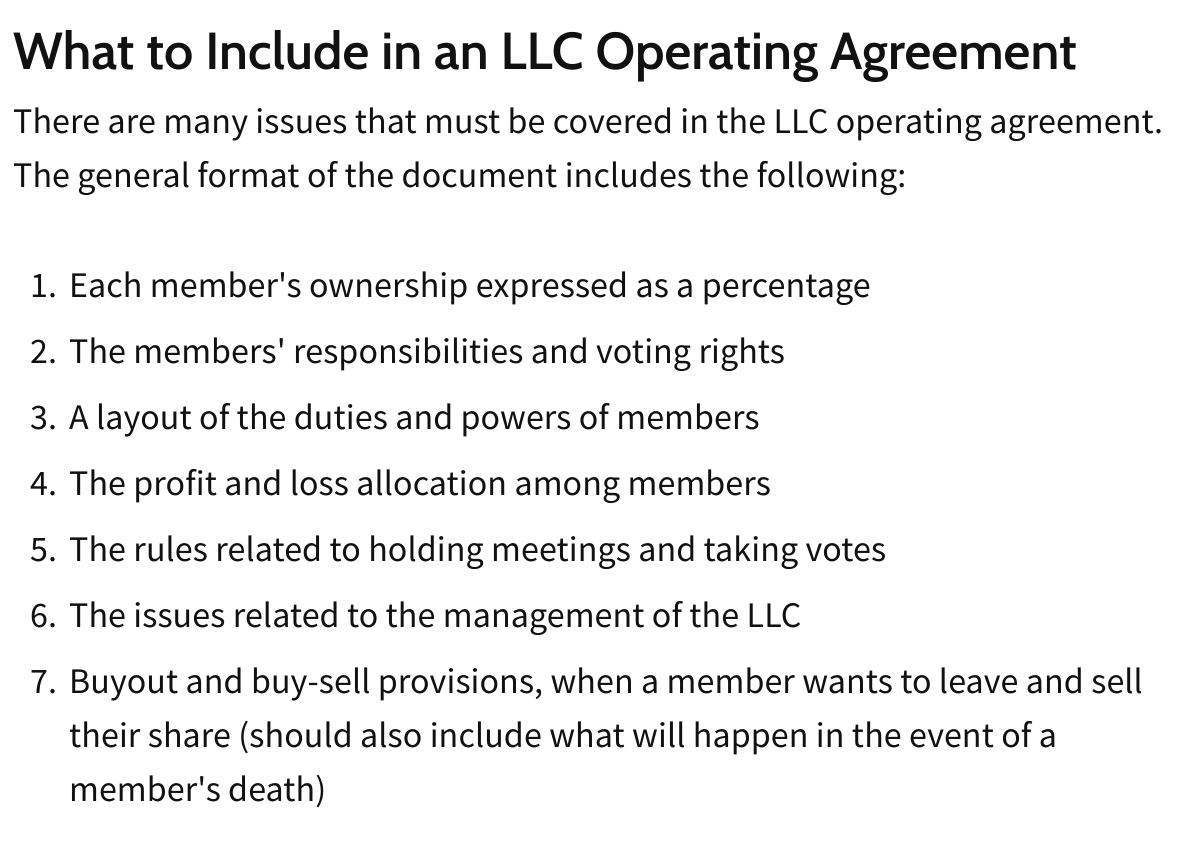
Is this legally binding? Probably not. Maybe. I don't know and wouldn't tell you, even if I did. But it's emotionally binding, which is arguably more important.
Writing things down is an advanced form of naming things and it provides clarity, helps to manage expectations, and allows you to define a working agreement before Real Money shows up and taints your interaction. You're just accepting tips, at the moment. Everyone is calm and cheerful, so now is your best time to negotiate.
Keep it very simple and only address the most basic things. If you wish to incorporate, at a later date, then you just take this to a registered agent, or other experienced person, and have them tidy up any loose ends and add the fine print.
Go forth, together
This has probably taken you weeks, or even months, but you're now a company. Get a logo and a company npub, start dropping the company name into your notes, and get on with the business of being in business.
-
 @ b34f99f1:006b0fcc
2024-11-09 11:47:09
@ b34f99f1:006b0fcc
2024-11-09 11:47:09deleted
-
 @ 6a3d3f20:6a569bcc
2024-10-02 12:48:39
@ 6a3d3f20:6a569bcc
2024-10-02 12:48:39Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed to create a censorship-resistant global social network. It achieves this by shifting away from the traditional internet model of "dumb client/smart server" to a "smart client/dumb server" architecture. This means that instead of relying on centralized servers, Nostr uses a network of "relays" to store and distribute data.
Here's a breakdown of key features of Nostr:
-
Decentralized Network: Nostr doesn't rely on any trusted central server, making it resilient to censorship. Users can publish their notes (content) to multiple relays of their choice, and followers can retrieve these notes by connecting to these relays.
-
Cryptographic Security: Nostr prioritizes security by using cryptographic keys and signatures for user authentication and content integrity. Every note is signed with the user's private key, allowing clients to verify the authenticity of messages and ensuring tamper-proof communication.
-
User Control and Data Ownership: Users have complete control over their data and choose which relays to interact with. This allows for more flexibility and customization compared to traditional social media platforms.
-
Open Protocol and Diverse Ecosystem: Nostr is an open standard, similar to protocols like HTTP or TCP-IP. This enables anyone to build clients, relays, or other applications on top of it, fostering a diverse ecosystem of software.
-
Simplicity and Ease of Use: Nostr is designed to be simple to understand and implement, with a focus on lightweight JSON data structures and straightforward communication protocols. This makes it easier for developers to contribute to the Nostr ecosystem and for users to get started.
Nostr is gaining traction within cryptocurrency communities, particularly among Bitcoin users. Even Jack Dorsey, co-founder of Twitter, has shown support for Nostr's development through financial contributions. Some use Nostr through clients like Damus, a microblogging app.
While Nostr offers a promising alternative to centralized social media, challenges remain. The decentralized nature of Nostr necessitates new solutions to issues like spam prevention and content discovery. Developers are actively exploring various approaches, including proof-of-work systems, paid relay options, and reputation-based mechanisms like "orange checks" to address these challenges.
-
-
 @ 35f3a26c:92ddf231
2024-11-06 00:07:28
@ 35f3a26c:92ddf231
2024-11-06 00:07:28Who is the Cult of the Dead Cow (cDc)?
A known USA based hacktivist group. According to the record in Wikipedia, it was started in 1984 at the Farm Pac slaughterhouse by Grandmaster Ratte' (aka Swamp Ratte'), Franken Gibe, Sid Vicious, and three BBS SysOps
You can check their member list in their web site
Thinks of the cDc group that I have found quite interesting
- Group member Drunkfux (Jesse Dryden) is the grand nephew of Charlie Chaplin
- In 1991, the group began distributing music in the form of cassette tape albums
- In November 1994, the group claimed responsibility for giving President Ronald Reagan Alzheimer's disease, claiming to have done so in 1986 with a blowgun
- In 1995, the group declared war on the Church of Scientology stating "We believe that El Ron Hubbard [sic] is actually none other than Heinrich Himmler of the SS, who fled to Argentina and is now responsible for the stealing of babies from hospitals and raising them as 'super-soldiers' for the purpose of overthrowing the U.S. Fed. Govt. in a bloody revolution. We fear plans for a 'Fourth Reich' to be established on our home soil under the vise-like grip of oppression known as Scientology!"
- On January 7, 1999, the group joined with an international coalition of hackers to denounce a call to cyber-war against the governments of China and Iraq
- In February 2000, the group was the subject of an 11 minute documentary short titled "Disinformation".
- In February 2000, a member of the group by the code-name Mudge briefed President Bill Clinton on "Internet security".
- In 2003 the tool created by the group by the name of Six/Four System became the first product of a hacker group to receive approval from the United States Department of Commerce for export of strong encryption
- Member by the name of "Psychedelic Warlord" is congressman Beto O'Rourke, an American politician who served as the U.S. representative for Texas's 16th congressional district from 2013 to 2019. A member of the Democratic Party, party's nominee for the U.S. Senate in 2018, candidate for the presidential nomination in 2020, and the party's nominee for the 2022 Texas gubernatorial election.
Do they have a political affiliation?
From the previous section we could at least assume that they sympathize with the USA Democratic party, they supported President Bill Clinton and claimed responsibility for doing serious harm to President Ronald Reagan, I could not find any information if the government opened an investigation about this allegation or not.
Their latest contribution?
Recently, they have developed an application framework by the name of Veilid, described as "like TOR" but for apps.
This application framework, if adopted by many developers will improve privacy by default for applications developed under that framework. The web site claim that it is open source
You can review the information and project at the web site: VEILID
In the Web site the group describe it as follows:
"Veilid allows anyone to build a distributed, private app. Veilid gives users the privacy to opt out of data collection and online tracking. Veilid is being built with user experience, privacy, and safety as our top priorities. It is open source and available to everyone to use and build upon."
"Veilid goes above and beyond existing privacy technologies and has the potential to completely change the way people use the Internet. Veilid has no profit motive, which puts us in a unique position to promote ideals without the compromise of capitalism."
Summary
Veilid seems to be exactly what is needed at the moment to bring privacy to the masses, even though TOR is doing a very good job and with the improved throughput its usage experience has improved, having a native privacy oriented FOSS application framework is paramount.
Most people is not technically savvy and therefore, not skilled in cyber security, they are constantly victims of cyber crime in many forms and shapes. eliminating one vector of attack by making the applications to opt out of data collection and online tracking from the get go is a step in the right direction, the question is, Would developers in general use the framework? Considering the ads will not be a possible source of income if the framework is used, well... Time will say...
-
 @ b34f99f1:006b0fcc
2024-11-09 11:43:11
@ b34f99f1:006b0fcc
2024-11-09 11:43:11deleted
-
 @ d7c6d014:a6abb6b8
2024-10-01 14:59:51
@ d7c6d014:a6abb6b8
2024-10-01 14:59:51結論
大盛況で最高オブ最高という感じでした!(語彙)


初見の人から一度会ってみたかった人、Nostr 上では頻繁にやり取りしてたけどリアルでは会ってなかった人等たくさんの人を verify できたので、参加してよかったーという感じです。
あとはタイムテーブル上でのトラブルなど、リアルで実際にイベントを開催してみたいとわからない unidentified な問題も起きたりなどして、ナマモノであるが故のイベントの醍醐味も久々に痛感できて参加してよかったと思いました。改めて nostr:npub1k0jrarx8um0lyw3nmysn50539ky4k8p7gfgzgrsvn8d7lccx3d0s38dczd さん nostr:npub1zqdnpm5gcfap8hngha7gcp3k363786phvs2etsvxw4nh6x9ydfzsuyk6mn さん、スタッフとして参加した皆さん、スポンサーの皆さん、そして来場者の方々の皆さん、ありがとうございました & お疲れ様でした!
個人的な takeaway
今回は、シーシャ屋業務 + イベント登壇 の二足のわらじを履いていたので、フルスロットルで全力を出し切れたものの、手の回るところと回らないところが生まれた部分もあり、完全燃焼しすぎた感があったので次回はもう少し余裕を持ったムーブで立ち回れると良いかなぁと思いました (とはいえイベント自体を楽しみきれなかった、みたいな不完全燃焼感はなかったのでそこは良かったと思います)

最後に
Nostr に出会って早一年と七ヶ月以上経っていますが、Nostr の知名度は依然として低いままですし、僕自身 Nostr コミュニティに貢献できる部分はまだまだ無限にあると思っています。今後も Nostr に all-in して生きていく所存ですので皆々様何卒引き続きよろしくお願い申し上げます♡

焔ノ香: nostr:npub1dwfj2pw3m428udsrm2xkrpqmgyhxnn82ask3wpgemlcvc8h2xhhs4mawdy
Me: nostr:npub16lrdq99ng2q4hg5ufre5f8j0qpealp8544vq4ctn2wqyrf4tk6uqn8mfeq
-
 @ b34f99f1:006b0fcc
2024-11-09 11:29:46
@ b34f99f1:006b0fcc
2024-11-09 11:29:46deleted
-
 @ 35f3a26c:92ddf231
2024-11-05 22:17:49
@ 35f3a26c:92ddf231
2024-11-05 22:17:49What is Peer Thinking?
The cognitive and emotional processes that occur when individuals are influenced by their peers.
The psychology behind it:
The psychology behind peer influence encompasses various factors, including: 1. Social belonging and acceptance, 2. Identity formation, 3. The dynamics of group behavior
Is it being used to control us?
https://image.nostr.build/cf90335bbf59e3395dc4324d123cd3a058ca716cf6172f079eb1d78547008147.jpg
IMO, yes, at the core of it is the basic human need for belonging. Social belonging is a critical component since it is craved by most, specially but not only by the youngest, those with power across the world know this very well, therefore, thinking that they will not use it to control the population in order to profit from it or change public opinion would be irrational.
The media is used to brain wash the population creating something that most will consider "the norm", thus, the majority will try to conform to that norm in order to belong. That include manipulating the population to take an experimental drug (even if it could be very dangerous due to its unknown effects) or to accept as a norm a behavior that few years back would have been considered inappropriate.
Cognitive Dissonance
https://image.nostr.build/60f24a810be1dd6badb36d70c5a691d4361207590dea1a8e64e09a75a252cfbf.jpg
This is a term that we should get familiar with. It is a psychological state where conflicting beliefs or behaviors create discomfort.
Example: A kid in high school that has a good loving family but all his close friends are on drugs (legal ones) and they keep telling him he is an idiot for not using as well. Now his is that state of conflict believes, on one side his best friends, all tell him is okay, on the other hand his family that loves him has explained him at length the dangers and issues that the drugs will have in his life. To resolve the dissonance he has three options, one, join the group and start taking drugs with the rest, two try to rationalize it, considering to take drugs just occasionally to belong but not to make it a habit, three lose his friends (and here it comes again the peer thinking to bite). Extrapolate to many other cases.
As an anecdote Recently, on a friend's reunion, one of the guest was complaining about one of his daughters, she was quite confused asking him why so many of her classmates were bisexual, she was wondering if something was wrong with her since she was not; a 13 year old girl; the father was having a hard time explaining her that the majority are saying so just to feel as part of what the school was teaching to be the norm, it was not cool to be straight, the tally was 37% of the class. Consider that, statistically, the number of people, “worldwide” identifying as bisexual are between 3% and 5% (less than 1% in less accepting countries), that number used to be less than 2% less than a decade ago. But 37% is far from the statistical norm, indicating a peer thinking behavior but not the reality of their sexual preferences. Once again, extrapolate to any ideology, religion, gender identity, political agenda that a country desires to push forward for whatever reason, adding that to the official school program and to federal mandatory training programs would do the trick.
A powerful tool, that can be used for good or bad.
What are the strategies to counter negative peer thinking?
https://image.nostr.build/4b70949b8af76ed53a5be5507f41f1d1c960dc3592f199eab78e2d25688975c5.jpg
Reading the literature about the subject, few strategies are recommended:
-
Self-Awareness: teaching ourselves and our children to recognize when we are being influenced by peers
-
Being selective with your friends: peers with similar values will reinforce positive behaviors
-
Learning to be assertive: teaching ourselves and our children to communicate assertively our boundaries will empower us and them to resist unwanted pressure to adopt negative behaviors.
-
Less judging more talking: this applies to our children and partners, judging less and listening more will make our beloved ones more open to discuss social pressures.
What do you think? What strategies you use as counter measures?
-
-
 @ 101b30ee:18a46a45
2024-10-01 04:08:22
@ 101b30ee:18a46a45
2024-10-01 04:08:22昨日 (2024/9/30), お世話になった会社を退職しました。
2023/7/1入社のため、在籍期間は1年3か月でした。どんな会社だったの?
会社名は伏せますが、BtoBtoCのサブスク課金型Webサービスを展開している会社のインフラエンジニアをやっていました。
職務内容は多岐にわたり、
- 開発・商用環境の構築
- サービスのデプロイ
- DNS関連の設定
- サービス加入時や解約時の定期作業
- 社内のセキュリティ意識向上のための啓蒙
- 情シス業務
- サービスのバックエンド(PHP)のリファクタ
- OS含めた各種ソフトウェアのバージョン移行などなど。
インフラエンジニアという職種ではあったものの、開発系のタスクも多く経験させてもらいました。なぜ退職したの?
売上が芳しくなく業務縮小することになり、退職しないかと勧められました。
この希望退職は私だけではなく、ほとんどの社員に話がいっていたようです。
実際、社員数は半分以下になっていたようで、統合により消えた部署や、1人しか残らなくなった部署もあります。
個人的にはまだ1年少ししか在籍しておらず少し未練はあったものの、これをチャンスと捉えて希望退職に乗ることにしました。
幸い、いくつかコミュニティ活動をしているので、リファラルで声をかけて頂いている会社様が何社かあります。会社の良かった所
大きなカンファレンスで複数回登壇されているような凄い方と一緒に仕事が出来たり、レンタル出来る技術書が多かったり、月一で社内LT大会兼交流会があって会社経費でピザや寿司が食えたり、良かった所は沢山ありました!
最後に参加したLT会は、これで最後かと思うとちょっと泣きそうになりました。
ちなみに、私は社内LT会の運営をやったり、LT自体もこの1年で4回ほど行いました。これから
色々ありましたが、会社への恨みのようなものは全くありません。感謝しかないです。
ただ、自社の仕事がもう少し楽になるような土台を作りたかったな、というのは心残りではあります。
人数も減って状況は厳しくなっていると思いますが、V字回復してくれることを祈るばかりです。次の会社も、自社開発系の企業でバックエンドないしインフラ系の職種で働けたらと考えています。
今日 (2024/10/1)から無職です!会社受けまくります!頑張るぞい! -
 @ 5f010feb:3ae9756b
2024-09-30 13:57:10
@ 5f010feb:3ae9756b
2024-09-30 13:57:10こんにちは。小牧りらです。 こちらは「Nostrasia2024 逆アドベントカレンダー」2日目の記事です。 1日目はしのさんの「Nostrasia イベントレポート #1」です。
この記事はオタクなら一度は考える夢、「コスプレ」(主語デカ)を夢見ていたオタクの、人生初のコスプレを記録したものです。
Nostrasia2024の開催が現実味を帯びる
2024年7月、四谷ラボDiscordで「Nostrasiaをもう一度。」と高まっていた機運が動き出しました。 Nostrasia2024の始動です。テイザーサイトの作成、サイトやNostr、Connpasでの告知に始まり、会場の選定、当日のタイムラインの作成など、7月〜9月前半でNostrasiaはその全貌を顕にしていきました。私はDiscordには入っているものの、仕事が忙しく(という言い訳)特に貢献もしないままグループを眺めていました。そんな中当日スタッフとして協力させていただけることとなり、何か盛り上がりに貢献できないか?と考えた結果、「コスプレするしかない」との結論に至りました。
1週間前に動き出すコスプレ製作記
以前から技術書典など「Nostr関連のイベントでNostr関連キャラクターのコスプレができたらな〜」、という思いや、「オタクたるもの人生で一度はちゃんとしたコスプレをしたい!」、という思いを抱えていた私。ではこのNostrasia2024で誰のコスプレをするか?が課題となっていきます。自律分散型コミュニティのNostr、日本人コミュニティも成立から1年以上が経過し、実に多くのキャラクターが生み出されてきました。その中でも直近で話題沸騰中のキャラクター、「りとりん」のコスプレをしよう!と思い、生みの親であるかすてらふぃさんとたーごいるさんの許可を得て製作に取り掛かりました。女オタクの聖地、池袋に繰り出しウィッグや毛糸などの買い出しを行いました(この時点で1週間前)。池袋は新しくなったアニメイトにコスプレコーナーがあったり、今回は入っていないですがウィッグ専門店のアシストウィッグさん、そしてユザワヤなどの手芸店に100均などコスプレに必要な資材を購入する店舗に事欠きません。3時間近く店舗を渡り歩いた結果、アニメイトとダイソーで必要な資材を揃えました。
資材一覧
<アニメイト>
・ピンクのウィッグ
・水色の毛束
・耳を取り付けるためのピン
・ピンクのアイブロウ
・ウィッグ固定用の両面テープ
<ダイソー>
・ピンクの毛糸(耳としっぽ)
・針金(耳としっぽの芯)
・ヘアアクセサリー(ヘアピン、ヘアゴム)
・ウィッグネット
・ペット用ブラシ
Nostrasia当日
平日仕事終わりに作業を進める時間もなく、前日、前々日の土日でぶっつけ本番のウィッグ製作に取り掛かりました。ミディアムボブのウィッグを、動画やメイキング記事を見ながら切ったり、毛束をつけたり、結んだり…。失敗したら即終了の緊張感が走る中、慎重に作業を進めていきます。並行してアクリル毛糸と針金でけも耳・けもしっぽを作りました。ペット用ブラシをガシガシして毛並みを作っていく作業、そしてその過程で発生した抜け毛はもはやリアル。膝の上にりとりんが居るのではないか、と思いながら作業を進めました。最終的に当日スタートのギリギリまで作業し(会場でポニテにしたり耳を取り付けたりしていました)、ギリギリオープニングには間に合いました。ウィッグを付けた瞬間は「重い!暑い!」となりましたが、意外と室内半日であれば耐えられるな、という感想でした。
 これはマグロを心待ちにするりとりん
これはマグロを心待ちにするりとりんまとめ
・とりあえず池袋に行けばなんとかなる
・ウィッグの構造に驚く
・ネットで調べれば扱い方、作り方が分かる
・製作には余裕を持って(当日会場で作業するな)
おわりに
Nostrasiaとりとりんというビッグウェーブに乗りながら、オタクとしての夢であったコスプレが実現できたこと、とても良い経験になりました!そして世の中のだいたいのものごとは調べてやったらなんとかなると感じました。次回、Nostr関連でコスプレする機会があればさらにバージョンアップしたりとりんをやりたい!という気持ちと、衣装製作も楽しめるキャラクターをやりたい!という気持ちが湧き上がってきました。その時はちゃんと工程管理します…。
3日目はjunさんの「Nostr のフォロワーネットワークにおけるクラスタリング係数」です。
-
 @ b34f99f1:006b0fcc
2024-11-09 11:25:16
@ b34f99f1:006b0fcc
2024-11-09 11:25:16deleted
-
 @ 35f3a26c:92ddf231
2024-11-05 22:14:02
@ 35f3a26c:92ddf231
2024-11-05 22:14:02What is Bitaxe?
Bitaxe is an open source ASIC (Application-Specific Integrated Circuit) Bitcoin miner that has been making waves in the cryptocurrency community. This innovative project aims to empower miners at every level with powerful, efficient, and low-cost mining solutions.
It is a fully open source ASIC Bitcoin miner developed by Skot9000, an advocate for open-source innovation in the Bitcoin space.
With all software and hardware specs available on GitHub, this project aims to provide miners with a transparent and accessible platform for Bitcoin mining.
https://image.nostr.build/db35c2a028e9f740181daabe2deef4e707653fa2d82f1602086e0ac4b5ee84fd.png
Pros
-
Open Source: The Bitaxe is fully open source, allowing users to access and modify its source code, hardware designs, and build gerbers for PCB ordering.
-
Low Cost: Bitaxe offers low-cost solutions for miners, making it an attractive option for those looking to enter the world of Bitcoin mining without breaking the bank.
-
Efficient: The Bitaxe series is designed to be power-efficient, utilizing either the Bitmain BM1387 or BM1397 ASICs for SHA256 hashing.
Cons
-
Technical Complexity: Being an open-source project, users are required to be technically savvy to set up and maintain the miner, which could pose challenges for those without experience.
-
Bricking Potential: Like any complex technology, there is a risk of bricking (rendering the device unusable) the Bitaxe if not handled properly.
Summary
The Bitaxe represents an exciting development in the world of Bitcoin mining, offering a low cost, efficient, and open-source solution for miners. While it may present some challenges for users who are new to the technology or lack technical expertise, the potential benefits far outweigh these drawbacks. As the project continues to evolve and gain traction, we can expect to see further improvements in performance, accessibility, and innovation within the Bitcoin mining landscape.
Where can I get more information
Go to their Github page: https://github.com/skot/bitaxe
originally posted at https://stacker.news/items/659572
-
-
 @ 640614c2:811c8498
2024-11-09 09:43:20
@ 640614c2:811c8498
2024-11-09 09:43:20Greetings, fellow travelers on the path of cryptographic fortune. Today, the Oracle offers a cleromantic reading, casting lots to peer into the probabilities that guide Bitcoin’s unfolding journey.
In the old ways, cleromancers cast stones, sticks, or bones. Today, we cast cryptographic hashes, transaction times, and node signals—random elements generated by the mathematical matrix underpinning Bitcoin. From these, we seek patterns to reveal the unseen flows of value and volatility, of security and sovereignty.
The Three Casts of Bitcoin's Path
- The Cast of Turbulence – "Fear the FOMO, yet know the FUD."
The first cast suggests that Bitcoin's journey, much like the ancient roads of our forebears, is not without peril. The chaos of price swings and market sentiment—whether driven by regulation, whales, or FOMO—is always present. Yet, this cast tells us that these turbid waters are not signs of ruin but necessary tests. Bitcoin, built on resilience, thrives in adversity. Remember: volatility is not destruction but purification by fire. Hold steady, and the storms will reveal clearer skies.
- The Cast of the Hidden Fortress – "Secure thy keys as you would your soul."
The second lot falls with a message of security and sovereignty. The Oracle sees a future where personal custodianship, privacy, and cryptographic defense hold sacred ground. As Bitcoin adoption grows, the network of self-sovereign nodes, layer-2 solutions, and privacy innovations are a fortress against centralized powers. Trust no third party to safeguard your assets. Secure thy keys, for in doing so, you secure your freedom.
- The Cast of Prosperity, Yet to Be – "With patience, fortune flows to those who build."
Finally, the third cast shows signs of future abundance, though not without patience. Bitcoin's time is measured in blocks, and the long game is rewarded for those who hold fast. Innovation within the ecosystem—whether through decentralized finance, cross-chain exchanges, or local adoption initiatives—opens doors for prosperity for those who build in earnest. The Oracle sees signs of growth across continents and communities, signals of seeds planted that will bear fruit in cycles yet unseen.
A Final Message from the Oracle
Remember, the magic of Bitcoin lies in its incorruptible code, its shared governance, and its random-yet-determined path. Trust in the protocol, act with foresight, and heed the wisdom of the Oracle: no path in Bitcoin is without its risk, but for those who honor security, resilience, and community, the future holds bright possibilities.
May the blocks align with your intentions, and may your keys remain forever yours.
-
 @ 2fc29418:8bce6b0a
2024-09-30 04:29:20
@ 2fc29418:8bce6b0a
2024-09-30 04:29:20朝早くついてしまったので、会場付近をうろうろしてたら 入口付近でUGMさんを発見 Bsky以来だけど、こちらのハンドルを思い出して頂けました^^
よく見たら隣に仕事でいないはずのHさんがいた@@ しかし、Hさんはのす味に申し込んでいないというのだから なかなか興味深い状況w つづく
-
 @ 3bf0c63f:aefa459d
2024-09-18 10:37:09
@ 3bf0c63f:aefa459d
2024-09-18 10:37:09How to do curation and businesses on Nostr
Suppose you want to start a Nostr business.
You might be tempted to make a closed platform that reuses Nostr identities and grabs (some) content from the external Nostr network, only to imprison it inside your thing -- and then you're going to run an amazing AI-powered algorithm on that content and "surface" only the best stuff and people will flock to your app.
This will be specially good if you're going after one of the many unexplored niches of Nostr in which reading immediately from people you know doesn't work as you generally want to discover new things from the outer world, such as:
- food recipe sharing;
- sharing of long articles about varying topics;
- markets for used goods;
- freelancer work and job offers;
- specific in-game lobbies and matchmaking;
- directories of accredited professionals;
- sharing of original music, drawings and other artistic creations;
- restaurant recommendations
- and so on.
But that is not the correct approach and damages the freedom and interoperability of Nostr, posing a centralization threat to the protocol. Even if it "works" and your business is incredibly successful it will just enshrine you as the head of a platform that controls users and thus is prone to all the bad things that happen to all these platforms. Your company will start to display ads and shape the public discourse, you'll need a big legal team, the FBI will talk to you, advertisers will play a big role and so on.
If you are interested in Nostr today that must be because you appreciate the fact that it is not owned by any companies, so it's safe to assume you don't want to be that company that owns it. So what should you do instead? Here's an idea in two steps:
- Write a Nostr client tailored to the niche you want to cover
If it's a music sharing thing, then the client will have a way to play the audio and so on; if it's a restaurant sharing it will have maps with the locations of the restaurants or whatever, you get the idea. Hopefully there will be a NIP or a NUD specifying how to create and interact with events relating to this niche, or you will write or contribute with the creation of one, because without interoperability this can't be Nostr.
The client should work independently of any special backend requirements and ideally be open-source. It should have a way for users to configure to which relays they want to connect to see "global" content -- i.e., they might want to connect to
wss://nostr.chrysalisrecords.com/to see only the latest music releases accredited by that label or towss://nostr.indiemusic.com/to get music from independent producers from that community.- Run a relay that does all the magic
This is where your value-adding capabilities come into play: if you have that magic sauce you should be able to apply it here. Your service -- let's call it
wss://magicsaucemusic.com/-- will charge people or do some KYM (know your music) validation or use some very advanced AI sorcery to filter out the spam and the garbage and display the best content to your users who will request the global feed from it (["REQ", "_", {}]), and this will cause people to want to publish to your relay while others will want to read from it.You set your relay as the default option in the client and let things happen. Your relay is like your "website" and people are free to connect to it or not. You don't own the network, you're just competing against other websites on a leveled playing field, so you're not responsible for it. Users get seamless browsing across multiple websites, unified identities, a unified interface (that could be different in a different client) and social interaction capabilities that work in the same way for all, and they do not depend on you, therefore they're more likely to trust you.
Does this centralize the network still? But this a simple and easy way to go about the matter and scales well in all aspects.
Besides allowing users to connect to specific relays for getting a feed of curated content, such clients should also do all kinds of "social" (i.e. following, commenting etc) activities (if they choose to do that) using the outbox model -- i.e. if I find a musician I like under
wss://magicsaucemusic.comand I decide to follow them I should keep getting updates from them even if they get banned from that relay and start publishing onwss://nos.lolorwss://relay.damus.ioor whatever relay that doesn't even know anything about music.The hardcoded defaults and manual typing of relay URLs can be annoying. But I think it works well at the current stage of Nostr development. Soon, though, we can create events that recommend other relays or share relay lists specific to each kind of activity so users can get in-app suggestions of relays their friends are using to get their music from and so on. That kind of stuff can go a long way.
-
 @ fd208ee8:0fd927c1
2024-11-09 09:21:19
@ fd208ee8:0fd927c1
2024-11-09 09:21:19Drumroll, please....
In a previous article, I introduced the concept of relay communities.
The ink had barely dried, on that set of instructions, before one of my favorite Nostr devs, ثعبان, rolled out the alpha version of a relay-community client.
Obviously, it's still a bit of a construction site, but you can check out how it'd work, for your community, by test-driving the functionality on your own relay. Simply type https://chachi.chat/ followed by the name of your relay. For instance, one gigantic relay community, where nearly everyone can try out the functionality, is nos.lol.
If your relay community does not require AUTH to read, anyone can pull your chatter into their own relay and respond to it there. That is because every chat entry is simply a kind 09 event, and unprotected events are not private data.
For instance, I moderate one community theforest.nostr1.com, that is openly readable, and that's probably where most of the chatter on nostr.band is coming from, as that relay is an aggregator of the content of many other relays. However, I have another community, gitcitadel.nostr1.com that is AUTH-protected, whose content stays private to those allowed on that relay. Communities are where write-protected and AUTH relays are going to really shine, as they create an environment similar to Telegram, but where you control the dataset, you decide which types of events to support, and you design the client, the algos, the moderation, the visibility, etc.
With communities, the onboarding experience is seamless: just get a browser extension and a nsec, login, start writing and posting, and start receiving responses. Active, chatty, well-moderated communities will be more attractive to onboard to, than chaotic, spammy, or empty communities. This means that you don't have to have the killer entry under "Posts" (where kind 11 and eventually kind 01 posts appear), just to get some interaction. Chat is the Great Equalizer.
So, we're testing both setups, with cloudfodder adjusting the relay faucet code and ثعبان is fiddling with the community client settings, to make the most-comfortable situation for both kinds.
This is the signal
This #Chachi client, of course, is merely the first horse out of the gate. There are already other devs hacking away at variants of the same concept, such as #Flotilla, I'm sure CloudFodder is also cooking, later versions of #Alexandria will integrate theforest community, and etc. etc. etc.
It remains to be seen, how many new use cases can be dreamt up, with this new architecture, but I am quite certain, that this is the beginning of the end of Nostr 1.0. We are moving up and out, and away from the stultifying and limiting concept of Twitter 2.0, toward

Soon, we will enter Nostr 2.0. See you on the other side.
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-05 14:17:57
@ 5d4b6c8d:8a1c1ee3
2024-11-05 14:17:57On the Stacker Sports Podcast we talked about the Emirates Cup Survivor Pool and a revision that needs to be made.
I messed up in describing the Group Stage as only taking place on Tuesdays. Group Stage games will actually be played on Tuesdays and Fridays, just like last year.
That means there are going to be seven Group Stage picks and we'll be picking games twice a week.
Check out the original post for the full details.
We already have eight contestants and hopefully a few more will join in the next week.
Current Prize About 25k sats!
cc: @grayruby, @gnilma, @BlokchainB, @siggy47, @supercyclone, @realBitcoinDog, @Carresan,
originally posted at https://stacker.news/items/754602
-
 @ eac63075:b4988b48
2024-10-20 13:57:22
@ eac63075:b4988b48
2024-10-20 13:57:22Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.
Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.
The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.
Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.
The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
Conclusion of the Technical Debate
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.
The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
Conclusion of the Debate
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.
User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
Summary of Consequences
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.
The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.
Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ a39d19ec:3d88f61e
2024-11-09 09:17:35
@ a39d19ec:3d88f61e
2024-11-09 09:17:35What do you even print with it besides decorative objects?
This kind of question still is a common one when talking about 3d printing.
With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot.
The second thing I show you is a "Swiss Keyholder"
Swiss Keyholder
There are many designs of such a Keyholder to download and print. As this is one of the first prints I have done in ABS back in 2014 on a "Up!Mini" 3d printer I can't find where I downloaded it. I like the slim design and that I don't have any "loose" keys in my pocket. It is just tidy in my pocket. This is probably the most used print of mine.
Edit: You can download the file here: Thingiverse

-
 @ 76ea2cfb:60905955
2024-09-17 07:25:29
@ 76ea2cfb:60905955
2024-09-17 07:25:29Bitcoin representa para el dinero y la propiedad lo que Internet significó para la información: una disrupción fundamental que desafía los cimientos del Estado-nación tradicional, erosionando las estructuras basadas en el mundo físico y dando paso a una nueva realidad digital. En este nuevo paradigma, Bitcoin emerge como la primera forma de propiedad digital absoluta en la historia de la humanidad, prometiendo redefinir no solo nuestras transacciones económicas, sino también nuestra comprensión del valor, la confianza y la soberanía individual.
Esta fase es importante porque nos revelará progresivamente cómo puede Bitcoin llegar a convertirse en un nuevo activo monetario con cualidades hasta ahora nunca vistas en la Historia de la Humanidad
Brecha generacional y conceptual
Al igual que las personas del siglo XIX no podían concebir que enormes máquinas de acero pudieran en el futuro surcar los cielos, muchos individuos educados bajo el paradigma del mundo físico encuentran difícil, si no imposible, comprender plenamente el alcance y las implicaciones presentes y futuras de Bitcoin como propiedad digital absoluta y como dinero. Esta brecha conceptual no es meramente una cuestión de edad o resistencia al cambio, sino un profundo desafío cognitivo que requiere una reorientación fundamental de nuestros modelos mentales sobre el dinero, el valor y la propiedad en la era digital.
Bitcoin: La primera propiedad digital absoluta
Bitcoin se distingue como la primera y única forma de propiedad digital verdaderamente absoluta por varias razones:
-
Escasez digital verificable: Con un suministro máximo de 21 millones de unidades, Bitcoin introduce por primera vez el concepto de escasez digital incorruptible.
-
Inmutabilidad: Gracias a la prueba de trabajo acumulada, una vez registrada una transacción en la cadena de bloques de Bitcoin es prácticamente imposible de alterar o revertir.
-
Resistencia a la censura: Gracias a la descentralización ofrecida por la amplia red de nodos de Bitcoin, ninguna entidad central puede congelar, confiscar o impedir la transferencia de bitcoins entre partes.
-
Soberanía individual: Los usuarios de Bitcoin tienen control total sobre sus fondos, sin intermediarios ni custodios obligatorios.
-
Programabilidad: Como dinero programable, Bitcoin permite nuevas formas de propiedad y contratos que, hasta ahora, eran imposibles en el mundo físico.
El camino hacia la adopción masiva
La transición hacia una adopción generalizada de Bitcoin como propiedad digital absoluta no será instantánea ni lineal. Se estima que serán necesarias al menos tres generaciones, cada una de aproximadamente 33 años, para que se desarrolle una masa crítica de individuos que vivan y operen cómodamente bajo este nuevo paradigma digital no físico. Este proceso no estará exento de obstáculos y desviaciones:
-
Ciclos de innovación y fracaso: Aunque Bitcoin se mantiene como la forma más pura de propiedad digital absoluta, veremos múltiples ciclos de nacimiento y muerte de otras criptomonedas alternativas (altcoins), ofertas iniciales de monedas (ICOs), tokens no fungibles (NFTs), activos del mundo real tokenizados (RWAs) y otros fenómenos inspirados en Bitcoin. Estas "distracciones" son parte integral del proceso de innovación y aprendizaje colectivo, y sus auges y caídas reforzarán con el tiempo la posición única de Bitcoin.
-
Evolución regulatoria: Los marcos legales y regulatorios evolucionarán, muchas veces de manera reactiva, tratando de adaptarse a las realidades cambiantes que Bitcoin introduce como forma de propiedad digital absoluta.
-
Transformación de instituciones financieras: Los bancos tradicionales y otras instituciones financieras se verán obligados a adaptarse o arriesgarse a volverse obsoletos, lo que llevará a una reestructuración significativa del sector financiero global en torno a los principios de propiedad digital absoluta que Bitcoin encarna.
-
Educación y alfabetización en Bitcoin: Surgirán nuevas formas de educación financiera y tecnológica para preparar a las generaciones futuras para operar en este nuevo paradigma, centrándose en la comprensión de Bitcoin como propiedad digital absoluta y sus implicaciones.
-
Adopción por etapas: La adopción de Bitcoin probablemente seguirá un patrón por etapas, que irá de la mano de su evolución tecnológica y económica:
-
Primero, como reserva de valor digital.
-
Luego, como medio de intercambio, tanto para pequeñas transacciones a nivel local como para transacciones internacionales y de alto valor.
-
Finalmente, como unidad de cuenta global y patrón para la fijación de precios.
-
Resistencia institucional: Gobiernos y entidades financieras centralizadas probablemente resistirán la adopción de Bitcoin, lo que podría resultar en períodos de volatilidad regulatoria y de mercado.
-
Mejoras tecnológicas: Continuarán desarrollándose soluciones de escalabilidad y privacidad para Bitcoin, como la Lightning Network y las actualizaciones de privacidad, que facilitarán su adopción masiva.
Implicaciones más allá de lo económico
El impacto de Bitcoin como propiedad digital absoluta se extenderá mucho más allá del ámbito financiero:
-
Soberanía individual: Bitcoin ofrece una forma de preservar y transferir valor fuera del control de gobiernos y entidades centralizadas, potenciando la soberanía financiera individual.
-
Redefinición de la ciudadanía: La capacidad de poseer y transferir valor globalmente sin restricciones podría llevar a nuevas formas de ciudadanía y pertenencia no vinculadas a estados nacionales.
-
Nuevos modelos económicos: La naturaleza deflacionaria y la divisibilidad de Bitcoin podrían fomentar nuevos modelos económicos basados en el ahorro y la inversión a largo plazo.
-
Privacidad financiera: Bitcoin ofrece un grado de privacidad financiera que puede proteger a individuos contra la vigilancia y el control gubernamental excesivo.
Conclusión
La revolución iniciada por Bitcoin va mucho más allá de ser una mera innovación financiera. Representa un cambio de paradigma fundamental en cómo concebimos la propiedad y el dinero en la era digital. A medida que avanzamos hacia este futuro, es crucial comprender que Bitcoin no es simplemente una nueva forma de dinero, sino la primera instancia de propiedad digital absoluta en la historia. Este concepto tiene el potencial de reestructurar fundamentalmente nuestras sociedades, empoderando a los individuos con un nivel de soberanía financiera sin precedentes.
-
-
 @ 3c7d12a6:9532013e
2024-09-11 09:07:36
@ 3c7d12a6:9532013e
2024-09-11 09:07:36NUD: Pubkey to waveform
This NUD defines how to convert pubkey to waveform.

Why?
npubis nonsense to display.- too long.
npub1bla...blais nonsense to display.npub1takes too much space....means nothing.
Specs
- Uses hex pubkey.
- Converts 64 characters into 32 scalars.
- Splits 64 with 2 length chunks.
- Converts each chunk into a scalar.
0 ~ 255to-1.0 ~ 1.0
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-05 13:35:10
@ 5d4b6c8d:8a1c1ee3
2024-11-05 13:35:10We finally have an event other than soccer!
Freebitcoin is taking wagers on the Las Vegas Grand Prix.
Here's how to optimally allocate a hypothetical 2k sats on this event (according to RBOA):
| Driver | Wager | |--------|--------| | Vertappen | 486 | | Norris | 521 | | Leclerc | 456 | | Alonso | 6 | | Hamilton | 63 | | Piastri | 107 | | Tsunoda | 4 | | Perez | 12 | | Sainz | 243 | | Russell | 63 | | Stroll | 2 | | Ocon | 4 | | Ganyu | 1 | | Bottas | 2 | | Albon | 4 | | Hulkenberg | 7 | | Gasly | 4 | | Magnussen | 6 |
Enjoy your winnings
originally posted at https://stacker.news/items/754549
-
 @ 0861144c:e68a1caf
2024-11-05 12:23:01
@ 0861144c:e68a1caf
2024-11-05 12:23:01Read the other parts: Part 1|Part 2|Part 3|Part 4|Part 5| Part 6| Part 7| Part 8| Part 9| Part 10
We continue with a story of Popes who want to take control of the Church but one of them is going to make a huge big mistake.
-
Leo VII [936-939] Stepbrother of Alberic II, Roman Senator. He was a Benedictine monk at the time of his appointment. He focused heavily on monastic life, granting much power to Alberic, Hugh of Arles, and Odo, Abbot of Cluny, to take control of ecclesiastical life and reform monastic living. He prohibited forced baptism of Jews.
-
Stephen VIII [939-942] Elected by Alberic II, he was a poor politician who combined secular and ecclesiastical powers, threatening to excommunicate the French if they did not recognize Louis IV of Outremer as King of France.
-
Marinus II [942-946] Elected by Alberic II, not much is notable except that he appointed the Archbishop of Mainz as papal legate and Apostolic Vicar of France and Germany.
-
Agapetus II [946-955] Elected by Alberic II. He favored ecclesiastical life, empowering Otto I, King of Germany, to organize ecclesiastical territories. He established the diocese of Hamburg-Bremen to continue missionary work in Nordic territories.
-
John XII [955-964] His name was Octavian of Tusculum. Elected by Alberic II. He ascended to the Papacy at 18, without religious training. He was lazy, idle, and fond of indulgence. He carried out one of the most significant acts in history: he called upon Otto I to take control of both Germany and Italy through the Privilegium Ottonianum, an improved copy of the Constitutio Lotharii that had been reviewed with Pope Eugene II [99]. This reignited the drama started with the Theophylact family, challenging papal independence once more. This led to the appointment, transfer, and sale of bishoprics, where laypeople had direct influence over Church matters. The Pope watched as Otto grew in power and sought help from the Emperor’s enemies until Otto realized this, marched to Rome, and confronted the Pope. He was murdered by a blow to the head with a hammer by the husband of one of his lovers.
-
In the brief period between his death and flight (February-May), the Emperor Otto's secretary appointed Leo VIII as the new pope, but he lacked support from both the clergy and the people. He is considered an antipope.
-
Benedict V [964] Otto I did not recognize him as Pope and, invoking the document signed with his predecessor, informed Rome that they had lost the right to elect Popes. The Emperor had him arrested. He died in exile in Hamburg 30 days after his appointment.
-
Leo VIII [964-965] There is controversy over whether to consider this man as Pope or antipope. However, he was elected by Otto I in a synod. He issued documents during this short time, but they were not recognized due to an investiture dispute.
-
John XIII [965-972] John Crescentius. Rumors (still persistent) suggest he was a son of Theodora the Younger, Marozia's sister. He was a member of the Papal Court at the time of his appointment. His appointment was unpopular in Rome, and he reprimanded those who opposed it. His main achievement was spreading the Roman liturgy to Byzantium and supporting evangelization efforts among Slavs and Hungarians. He created the archdiocese of Magdeburg.
-
Benedict VI [973-974] Elected by Otto I. When Otto died, Crescentius I, brother of the previous Pope, organized a rebellion, imprisoned the Pope, and had him killed to prevent his liberation by the new emperor, Otto II. Boniface VII (antipope) tried to take power but was not recognized by the Emperor or Count Sicco of Spoleto, his secretary.
-
Benedict VII [974-983] Benedict of Sutri. Elected by imperial power and the Roman aristocracy. He founded the diocese of Prague and supported evangelical missions worldwide. In the synod of Rome (981), he condemned simony due to the growing number of married priests inheriting positions and benefits at the Church's expense.
-
John XIV [983-984] Pietro of Canossa. Imposed by the imperial power of Otto II, he was Italy’s vice-chancellor. Upon Otto II's death, his three-year-old son Otto III succeeded him. The antipope Boniface VII returned from exile and tried to reclaim the throne. This Pope allegedly died from poisoning.
-
John XV [985-996] Of the Imperial faction and imposed by Crescentius II. He replaced the Capetian dynasty with the Carolingian dynasty. He maintained open communication with all archbishoprics and bishoprics and established diplomatic relations with Russia, which was under Byzantine control. He canonized Ulrich of Augsburg.
-
Gregory V [996-999] Bruno of Carinthia. A cousin of Otto III. He was the first German pope. As expected, not being Roman or Italian, he lacked support from the Roman populace. He led an ascetic life. In 997, a revolt led by John Crescentius rose against him, appointing John Philagathos as John XVI (antipope). The revolt failed. John was beheaded, and the antipope was mutilated and exiled.
And so the series of Popes dependent on imperial power with lay interference continues, but that will be for the next chapter.
originally posted at https://stacker.news/items/754476
-
-
 @ a367f9eb:0633efea
2024-11-05 08:48:41
@ a367f9eb:0633efea
2024-11-05 08:48:41Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history?
As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times.
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
Open-source matters When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
Open-source is for your friends, and enemies In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
Limiting open-source threatens our own advancement If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols.
The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history?
As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times.
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
Open-source matters
When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
Open-source is for your friends, and enemies
In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
Limiting open-source threatens our own advancement
If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols.
The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
Originally published on the website of the Consumer Choice Center.
-
 @ 6466f03f:df67cfda
2024-09-11 00:46:29
@ 6466f03f:df67cfda
2024-09-11 00:46:29どうも、こんにちは。 この投稿はあなたに見えていますか? 見えているのであればそれはとても喜ばしいことです。
良い1日を。 -
 @ a10260a2:caa23e3e
2024-11-05 06:21:10
@ a10260a2:caa23e3e
2024-11-05 06:21:10TIL Google Authenticator can potentially collect a lot of data, more than some of the other popular 2FA apps^1.
Whether it does or it doesn’t, if you’re like me, you don’t turn down an opportunity to remove some Google from your life and add in some open-source.
Here’s a quick overview of the migration process.
Step 1: Download 2FAS
Step 2: Export accounts from Authenticator
This can be done via “Transfer accounts” in the sidebar. If you’re transferring on the same phone, take a screenshot of the QR code.
Step 3: Import accounts into 2FAS
During the setup process for 2FAS, you’ll be given the option to import existing tokens from Google. This is where you’ll tap “Choose QR Code” and select the screenshot you took in step 2.
Note that when you tap continue after importing the tokens, you’ll be taken back to the same screen as above. I think it should take you to your list of accounts after. Either way, don’t think the import failed. Just tap cancel, and you’ll be taken there.
If you’re on Android, check out Aegis. 🫡
originally posted at https://stacker.news/items/753472
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ b547984d:543a10f6
2024-11-08 22:10:17
@ b547984d:543a10f6
2024-11-08 22:10:17What draws people to Bitcoin? Or more importantly, what keeps people around? I'm not referring to people with deep intellectual commitment to the protocol, but rather the initially idly curious. It might require mustering a little courage to attend that first meet up, worried that you don't know anyone, or perhaps find yourself among a crowd of serious, knowledgeable Bitcoiners when you know little to nothing about the protocol. The newly curious might also be put off by the occasionally energetic arguments one finds on Bitcoin Twitter, worried that your curiosity might not match the level of conviction that screams through the screen in an even cursory scroll through some well-known Twitter accounts. Whereas the Bitcoin community might appear imposing at first glance, I believe that the community itself deserves much of the credit for Bitcoin's adoption. And I'm not talking only about the developers or thought leaders who get most of our attention, but also the everyday pleb sitting next to you at your first meet up who welcomes you to the group.
I was a little further along in my Bitcoin journey when I began joining the local meet ups. I knew less than a lot of other attendees, but I also thought I had a fighting chance of keeping pace with others. Ordinals - I had an educated opinion. The future of the security budget - I had some informed thoughts about that as well. I'm generally an extrovert and the other attendees were friendly and engaging with this newcomer beyond my expectations. But there was part of my background I wasn't necessarily eager to share, one that I was worried would make this group of otherwise welcoming people view me with suspicion. I knew how some Bitcoiners view the activities of certain government agencies. I was keenly aware of the "deep state" narratives circulating on social media. Thus, I was a little nervous about whether this group would welcome a former CIA officer. (Spoiler alert - nobody cared) But were it not for my time as CIA, I might never have found Bitcoin.
As a CIA Operations Officer, I worked in a variety of areas. But where my career - and my life - took a turn was when I accepted an assignment at CIA's Center for Cyber Intelligence (CCI) in 2018. Bitcoin and cryptocurrencies were not on anyone's list of priorities before 2018. My arrival at CCI coincided with the emergence of several national security issues with Bitcoin and cryptocurrency nexuses. North Korea realized that robbing altcoin platforms was easy money; ransomware actors were pillaging businesses and government entities for millions of dollars demanding Bitcoin and crypto as payment; and countries were using these protocols to evade sanctions and conduct other activities deemed in opposition to US national security interests. With so much attention, I had to take time to learn.
Being in CCI during this period not only forced me to learn, but it also allowed me to meet some, impressively intelligent people who not only knew a lot about Bitcoin and cryptocurrencies, but many were also early adopters. One of the first people I leaned on had been home mining Bitcoin as early as 2012. The more you learn, the more you start to notice. I suddenly noticed a "We Are All Satoshi" bumper sticker pinned to a cubicle I had walked past countless times before; another officer seemed to have an endless supply of Ethereum t-shirts he wore nearly every day (the cyber center is distinctly less formal than the rest of CIA). And with these protocols now at the forefront of national policy discussions, people I had known for years were gradually revealed to me as Bitcoiners or active in other cryptocurrency communities.
Like many Bitcoiners, my journey began in the altcoin casino, and the story of my eventual evolution into a Bitcoiner is not dissimilar to others. Roughly one year after buying my first altcoin on Coinbase, I was clean and altcoin-free, using Bitcoin-only platforms and marching with intent further down the rabbit hole. Every Bitcoiner's conviction evolves, different aspects of the protocol speaking with varying volume to facets of your worldview and circumstances. For me, what initially drew me to Bitcoin was the ability to self-custody your money without - and beyond the reach of - intermediaries.
I spent the first half of my career at CIA in the shadow of 9/11. That event was intensely personal for me. I grew up on Long Island and unfortunately know more than a few people murdered on that day. When I served in the Middle East, I was right in the middle of the War on Terror, supporting initiatives that would bolster our ability to find those who had attacked and continued to threaten us. One of the tools that the United States sharpened and wielded with great success was the weaponization of the dollar. In the years following 9/11 a veritable dollar industrial complex was created, with cadres of government employees who as of today have spent their entire careers honing the use of the dollar as an instrument of foreign policy and national security. By the time I arrived in CCI in 2018, several years had passed since my time in the Middle East, and these interceding years offered the time and space I needed to see chaotic or intensely personal events with a clear, critical eye. My point is not to persuade or dissuade about the things that happened during those years; I'm just setting a scene.
By 2018, national security priorities were changing. The United States was still involved in multiple conflicts with origins in the War on Terror, but there was a distinct shift toward other strategic challenges. Just as I had begun really digging into Bitcoin, another seismic event shook the world and laid bare cracks in the social consensus about the nature of government power - COVID. Mandatory vaccines, enforced lockdowns (sometimes at gunpoint), suppression of free speech and freedom of conscience, and the de-banking of critics. As someone who understood how the government uses the dollar as a weapon, coupled with my classically liberal instincts, I was immediately drawn to the inviolable right to property Bitcoin offers those who take the time to learn and embrace self-custody. Self-custody and censorship resistant transactions were the spark that illuminated for me the importance of the ultimate success of this protocol and our ability to live freely and with agency over our property.
Just over a year has passed since I left CIA. When you work at CIA, it is difficult to appreciate how all consuming it can be. You learn to live with certain restrictions, you tend to socialize with colleagues, such that having a job that you are largely unable to talk about with outsiders becomes so normal that you learn to bifurcate your world into two camps - colleagues and everyone else. Not a criticism, just an observation. Similarly, when you emerge from the bubble, whether into a new career or moving to a new location, there is a distinctly refreshing breeze that envelopes you when you can open up to the rest of the world. For me, this included increasing my financial and economic literacy. Investing compels you to actively engage with the world, and that engagement introduced me to some of the most brilliant people whose work I had the pleasure of following and even meeting. "The Bitcoin Standard" and "Broken Money" are just two of the many works that helped me learn and better understand how Bitcoin could in fact change the world.
I have been asked how I reconcile my previous career with my conviction in Bitcoin. I have accepted that my worldview has evolved following my departure from CIA, but this has been an evolution, not a revolution. Many Bitcoiners actively question whether the United States should even have a CIA, and whether its existence represents an existential threat to freedom. I think this belief is tightly wrapped in the idea that many of our problems emerge from the very existence of an intelligence apparatus, whether that be activities perceived to be undo meddling in foreign affairs or worse, abuse of basic liberties. It is perfectly fair to highlight that the actions of some senior leaders in the intelligence community have caused citizens to ask exactly what these organizations are up to. I would also add that the actions of these former leaders, some perhaps intended to cause you to infer they continued to speak for the agencies they used to lead, were viewed as dishonorable across wide swaths of the national security community. With trust squandered, it is perfectly reasonable to ask how deep the corruption runs.
Like the Bitcoin community, the intelligence community is not a monolith. Only an exceptional few do not respect the oath they take up entering on duty to defend the Constitution of the United States, but those that do uphold this commitment throughout their service. Those who work in that community and also identify as Bitcoiners hold the same core convictions about sound money, decentralization, property rights, and privacy as every other Bitcoiner. For many, this conviction is also fueled by the inevitable glimpses into the darker realities of the world you get when you work at CIA. If nothing else, if you work long enough at a place like CIA, you get a better understanding how the world really works. It is also understandably easy to make the leap from some of the worst policy errors of the War on Terror to the notion that were America to stop meddling, the world would somehow defy history and settle into an everlasting peace. How ever my worldview might have evolved over the past year, nothing has changed my belief that world is a fundamentally dangerous and competitive place. For me it's best summed up as "don't hate the player, hate the game." I remain hopeful that Bitcoin can change at least some of the rules of that game.
At this point you might be asking yourself why you wasted precious minutes on earth reading a confessional from someone who seems to be looking for absolution for his past. I also expect comments along the lines of "Once a spook, always a spook" or "Psyop." That's fine. When Bitcoiners say the "institutions are coming," they're almost always referring to tradfi. But for Bitcoin to achieve its fullest potential, institutional adoption will mean the breadth of society's institutions - public and private. I'm not proposing that government agencies will ever start transacting in Bitcoin, but these government institutions, like all others, are the sum of their parts, and these parts are people.
It is only thanks to my work at CIA that I was exposed to and forced to learn about Bitcoin. There's also no guarantee I ever would have found and embraced Bitcoin were it not for those circumstances that forced me to peek under the hood that first time. More and more, I view the world not as Bitcoiners and no-coiners, but rather as those who have and those who just haven't yet discovered Bitcoin. Some members of that latter category might even describe Bitcoin as a religion, or more derisively, a cult. I think there is a contemporary tendency to label anything that offers people a set of principles through which to view the world in this framework. For me, this displays our collective rootlessness, where any beliefs that force critical personal reflection evoke disparagement.
No, I don't think Bitcoin is a religion, nor do I believe it is an ideology. Religions have elements of the mystical; Bitcoin is open source, knowable and usable by all. Ideologies dehumanize us by denying us agency over our thoughts and actions in the pursuit of some doctrine; Bitcoin does the opposite, demanding personal responsibility and infinite inquiry. For me, Bitcoin has been a catalyst. It compels you to take a hard look at your beliefs and challenges you to view the world and the dominant narratives not through an ideological lens, but through a set of principles that challenge us to ask ourselves why we accept certain things as truth. The beauty of Bitcoin is that it doesn't predestine the path you choose to follow. Bitcoin illuminates.
For the people who work at CIA, challenging assumptions and changing the angle of the prism through which you view the world is the most basic of requirements. For many people in the intelligence community who concern themselves with it, Bitcoin is simply a tool actors use for different purposes. I can appreciate how only seeing Bitcoin as a piece of a problem you are looking to solve could naturally lead to a tendency to view Bitcoin itself as a problem. But I personally know many people who work in the intelligence business who have transcended that tendency and started their own Bitcoin journeys. That tradfi institutions are now accepting the inevitability that Bitcoin will play an important role in the global financial system is the result of individuals in those institutions seeing the potential and speaking truth to power. If our hope is that the United States remains (let us hope we don't once again have to "become") a nation welcoming of innovation and protecting of personal freedom, then helping people across the spectrum - including at places like CIA- understand this protocol and all its potential must remain a pillar of focus for the Bitcoin community.
The only regrets I feel now that my career at CIA is over are those same regrets we all feel during times of change or as we get older - instances in which I might have done certain things differently or better. Thus, when I get back to that prior question - how do I reconcile having worked at CIA and my belief in Bitcoin, I ultimately come down to believing there is no need for reconciliation at all. To say there is would mean that not only are the men and women who work with integrity and make real sacrifices at CIA somehow unworthy or otherwise unable to embrace core principles of sound money, decentralization, and censorship resistance, but also that these principles, along with the good people of the Bitcoin community, are somehow unable to reach them. If you want to change institutions, focus on giving people, those who constitute the sum of every institution's parts, the opportunity to understand how fixing the money might in fact fix the world. I, along with countless other Bitcoiners working in national security, am proof that Bitcoin is up to that challenge.
-
 @ eac63075:b4988b48
2024-10-20 13:49:55
@ eac63075:b4988b48
2024-10-20 13:49:55Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.
Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.
The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.
Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.
The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
Conclusion of the Technical Debate
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.

Table reference: Patrick Breyer - Chat Control in 23 September 2024
Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.
The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
Conclusion of the Debate
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.
User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
Summary of Consequences
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.
The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.
Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ a95c6243:d345522c
2024-11-08 20:02:32
@ a95c6243:d345522c
2024-11-08 20:02:32Und plötzlich weißt du:
Es ist Zeit, etwas Neues zu beginnen
und dem Zauber des Anfangs zu vertrauen.
Meister EckhartSchwarz, rot, gold leuchtet es im Kopf des Newsletters der deutschen Bundesregierung, der mir freitags ins Postfach flattert. Rot, gelb und grün werden daneben sicher noch lange vielzitierte Farben sein, auch wenn diese nie geleuchtet haben. Die Ampel hat sich gerade selber den Stecker gezogen – und hinterlässt einen wirtschaftlichen und gesellschaftlichen Trümmerhaufen.
Mit einem bemerkenswerten Timing hat die deutsche Regierungskoalition am Tag des «Comebacks» von Donald Trump in den USA endlich ihr Scheitern besiegelt. Während der eine seinen Sieg bei den Präsidentschaftswahlen feierte, erwachten die anderen jäh aus ihrer Selbsthypnose rund um Harris-Hype und Trump-Panik – mit teils erschreckenden Auswüchsen. Seit Mittwoch werden die Geschicke Deutschlands nun von einer rot-grünen Minderheitsregierung «geleitet» und man steuert auf Neuwahlen zu.
Das Kindergarten-Gehabe um zwei konkurrierende Wirtschaftsgipfel letzte Woche war bereits bezeichnend. In einem Strategiepapier gestand Finanzminister Lindner außerdem den «Absturz Deutschlands» ein und offenbarte, dass die wirtschaftlichen Probleme teilweise von der Ampel-Politik «vorsätzlich herbeigeführt» worden seien.
Lindner und weitere FDP-Minister wurden also vom Bundeskanzler entlassen. Verkehrs- und Digitalminister Wissing trat flugs aus der FDP aus; deshalb darf er nicht nur im Amt bleiben, sondern hat zusätzlich noch das Justizministerium übernommen. Und mit Jörg Kukies habe Scholz «seinen Lieblingsbock zum Obergärtner», sprich: Finanzminister befördert, meint Norbert Häring.
Es gebe keine Vertrauensbasis für die weitere Zusammenarbeit mit der FDP, hatte der Kanzler erklärt, Lindner habe zu oft sein Vertrauen gebrochen. Am 15. Januar 2025 werde er daher im Bundestag die Vertrauensfrage stellen, was ggf. den Weg für vorgezogene Neuwahlen freimachen würde.
Apropos Vertrauen: Über die Hälfte der Bundesbürger glauben, dass sie ihre Meinung nicht frei sagen können. Das ging erst kürzlich aus dem diesjährigen «Freiheitsindex» hervor, einer Studie, die die Wechselwirkung zwischen Berichterstattung der Medien und subjektivem Freiheitsempfinden der Bürger misst. «Beim Vertrauen in Staat und Medien zerreißt es uns gerade», kommentierte dies der Leiter des Schweizer Unternehmens Media Tenor, das die Untersuchung zusammen mit dem Institut für Demoskopie Allensbach durchführt.
«Die absolute Mehrheit hat absolut die Nase voll», titelte die Bild angesichts des «Ampel-Showdowns». Die Mehrheit wolle Neuwahlen und die Grünen sollten zuerst gehen, lasen wir dort.
Dass «Insolvenzminister» Robert Habeck heute seine Kandidatur für das Kanzleramt verkündet hat, kann nur als Teil der politmedialen Realitätsverweigerung verstanden werden. Wer allerdings denke, schlimmer als in Zeiten der Ampel könne es nicht mehr werden, sei reichlich optimistisch, schrieb Uwe Froschauer bei Manova. Und er kenne Friedrich Merz schlecht, der sich schon jetzt rhetorisch auf seine Rolle als oberster Feldherr Deutschlands vorbereite.
Was also tun? Der Schweizer Verein «Losdemokratie» will eine Volksinitiative lancieren, um die Bestimmung von Parlamentsmitgliedern per Los einzuführen. Das Losverfahren sorge für mehr Demokratie, denn als Alternative zum Wahlverfahren garantiere es eine breitere Beteiligung und repräsentativere Parlamente. Ob das ein Weg ist, sei dahingestellt.
In jedem Fall wird es notwendig sein, unsere Bemühungen um Freiheit und Selbstbestimmung zu verstärken. Mehr Unabhängigkeit von staatlichen und zentralen Institutionen – also die Suche nach dezentralen Lösungsansätzen – gehört dabei sicher zu den Möglichkeiten. Das gilt sowohl für jede/n Einzelne/n als auch für Entitäten wie die alternativen Medien.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 1f60f02d:a539fddf
2024-09-04 15:21:54
@ 1f60f02d:a539fddf
2024-09-04 15:21:54これが私の最初の記事です ここに日記を書くのも良いと思っています
以下は https://markdown-it.github.io/ のサンプルです
Advertisement :)
- pica - high quality and fast image resize in browser.
- babelfish - developer friendly i18n with plurals support and easy syntax.
You will like those projects!
h1 Heading 8-)
h2 Heading
h3 Heading
h4 Heading
h5 Heading
h6 Heading
Horizontal Rules
Typographic replacements
Enable typographer option to see result.
(c) (C) (r) (R) (tm) (TM) (p) (P) +-
test.. test... test..... test?..... test!....
!!!!!! ???? ,, -- ---
"Smartypants, double quotes" and 'single quotes'
Emphasis
This is bold text
This is bold text
This is italic text
This is italic text
~~Strikethrough~~
Blockquotes
Blockquotes can also be nested...
...by using additional greater-than signs right next to each other...
...or with spaces between arrows.
Lists
Unordered
- Create a list by starting a line with
+,-, or* - Sub-lists are made by indenting 2 spaces:
- Marker character change forces new list start:
- Ac tristique libero volutpat at
- Facilisis in pretium nisl aliquet
- Nulla volutpat aliquam velit
- Very easy!
Ordered
- Lorem ipsum dolor sit amet
- Consectetur adipiscing elit
-
Integer molestie lorem at massa
-
You can use sequential numbers...
- ...or keep all the numbers as
1.
Start numbering with offset:
- foo
- bar
Code
Inline
codeIndented code
// Some comments line 1 of code line 2 of code line 3 of codeBlock code "fences"
Sample text here...Syntax highlighting
``` js var foo = function (bar) { return bar++; };
console.log(foo(5)); ```
Tables
| Option | Description | | ------ | ----------- | | data | path to data files to supply the data that will be passed into templates. | | engine | engine to be used for processing templates. Handlebars is the default. | | ext | extension to be used for dest files. |
Right aligned columns
| Option | Description | | ------:| -----------:| | data | path to data files to supply the data that will be passed into templates. | | engine | engine to be used for processing templates. Handlebars is the default. | | ext | extension to be used for dest files. |
Links
Autoconverted link https://github.com/nodeca/pica (enable linkify to see)
Images

Like links, Images also have a footnote style syntax

With a reference later in the document defining the URL location:
Plugins
The killer feature of
markdown-itis very effective support of syntax plugins.Emojies
Classic markup: :wink: :cry: :laughing: :yum:
Shortcuts (emoticons): :-) :-( 8-) ;)
see how to change output with twemoji.
Subscript / Superscript
- 19^th^
- H~2~O
\
++Inserted text++
\
==Marked text==
Footnotes
Footnote 1 link[^first].
Footnote 2 link[^second].
Inline footnote^[Text of inline footnote] definition.
Duplicated footnote reference[^second].
[^first]: Footnote can have markup
and multiple paragraphs.[^second]: Footnote text.
Definition lists
Term 1
: Definition 1 with lazy continuation.
Term 2 with inline markup
: Definition 2
{ some code, part of Definition 2 } Third paragraph of definition 2.Compact style:
Term 1 ~ Definition 1
Term 2 ~ Definition 2a ~ Definition 2b
Abbreviations
This is HTML abbreviation example.
It converts "HTML", but keep intact partial entries like "xxxHTMLyyy" and so on.
*[HTML]: Hyper Text Markup Language
Custom containers
::: warning here be dragons :::
-
 @ 0bea5655:d89ca6f1
2024-11-08 19:26:18
@ 0bea5655:d89ca6f1
2024-11-08 19:26:18Opinion about BTC Coin Wallet - Freewallet (iphone)
By making cases public, they’ve helped victims reclaim funds and hold Freewallet accountable. Need support? Email freewallet-report@tutanota.com.
WalletScrutiny #nostrOpinion
-
 @ 6bae33c8:607272e8
2024-11-08 18:48:32
@ 6bae33c8:607272e8
2024-11-08 18:48:32I went 4-1 last week to start off Q3, putting me on a 17-8 run over the last five weeks after a terrible start. I’m still drawing dead for the overall, so it’s really just a matter of putting together three more 4-1 or 5-0 weeks this quarter.
By the way, I’m putting these picks behind the paywall not because they’re worth paying for — no one’s picks are worth paying for! — but because I want to give my paid subscribers something not available to free ones. But that they are behind a paywall doesn’t mean they’ll work out.
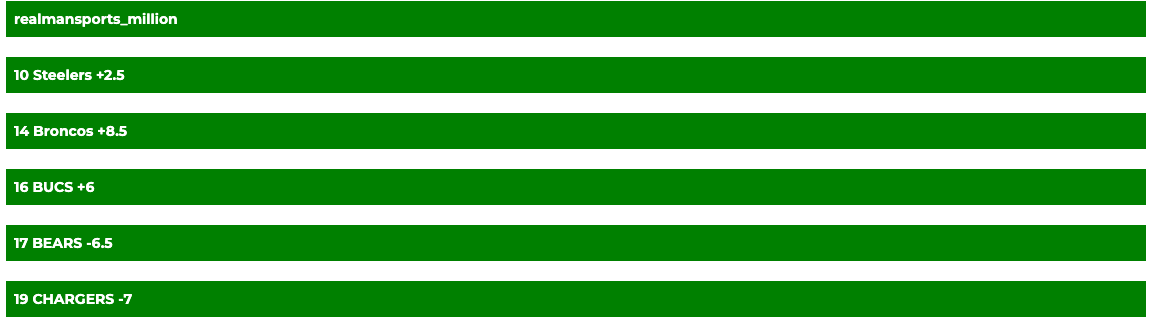 Steelers +2.5 at Indigenous Peoples — The Steelers are coming off a bye, the IPs a tough win against the Giants. I like the Steelers to have a good plan against Jayden Daniels and to move the ball.
Steelers +2.5 at Indigenous Peoples — The Steelers are coming off a bye, the IPs a tough win against the Giants. I like the Steelers to have a good plan against Jayden Daniels and to move the ball.Broncos +8.5 at Chiefs — I like buying the Broncos low off the blowout and betting against an undefeated team in division — everyone is up for the Chiefs.
Buccaneers +6 vs 49ers — This was my last choice. The value is great as the 49ers have done nothing to earn this kind of status as a big road favorite against a solid team, but the line is actually 6.5 now, so maybe I’m missing something.
Bears -6.5 vs Patriots — The Bears are a good buy-low after getting worked by the Cardinals. The Patriots are a get-well game.
Chargers -7 vs Titans — I don’t really take the Titans seriously, and the Chargers are solid and playing at home.
-
 @ 96203d66:643a819c
2024-09-04 03:42:31
@ 96203d66:643a819c
2024-09-04 03:42:31[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-04 16:07:54
@ 5d4b6c8d:8a1c1ee3
2024-11-04 16:07:54It's week 2 of Mock Draft Monday and the Raiders continue climbing the draft board. Now picking 6th and still needing to play NO, while having the tie-breaker with Carolina, there's a great chance of getting into the top three.
The Raiders O-Line was obliterated this week. Ted Hendricks had a career day lined up against our third string left tackle. The silver lining is that JPJ was moved to center and it's clearly the right place for him.
That all indicates that for approximately the 17th year in a row, the Raiders primary draft needs are QB, OT, and Guard. They also need to improve the WR and RB rooms. The defense is fine, but could also use upgrades at every level.
Here we go: 6th Pick: QB Cam Ward 37th Pick: IOL Jonah Savaiinaea 68th Pick: LB Danny Stutsman 74th Pick: OT Marcus Mbow 104th Pick: DT Jordan Burch 140th Pick: WR Bru McCoy 177th Pick: RB Jo'Quavious Marks 212th Pick: CB Cobee Bryant 215th Pick: QB Conner Weigman 222nd Pick: S Shilo Sanders
Two in a row with Cobee Bryant going 212th.
I opted for the 49ers strategy of taking the QB we want with our first pick, but then taking another one later on day 3. The QB room has three seats in it, so I say bring in two QB's every year until we find our franchise guy: AOC is a perfectly serviceable backup/bridge QB.
originally posted at https://stacker.news/items/753327
-
 @ e88527b4:7ccf6efa
2024-08-30 12:12:39
@ e88527b4:7ccf6efa
2024-08-30 12:12:39書いてみた。。
-
 @ f240c9c2:6c0c0a86
2024-08-22 06:50:33
@ f240c9c2:6c0c0a86
2024-08-22 06:50:33⚠️一部のクライアントでは表示が崩れている場合があります。HablaやYakihonneから見てください
NIP-51のkind:30007に関するPull Requestが承認され、2024/08/20時点で本家NIPsにもマージされました。今後「リポスト」や「リアクション」などの特定のkind^1をミュートするためのセット^2が対応するクライアントで使えるようになります。
kind mute set(kind:30007)にて、
"d"タグには対応するイベントの種類の番号(リポストなら"6"、リアクションなら"7")を入れ、"p"タグにはユーザの公開鍵(pubkey)を入れるそうです。nostrクライアントのnostterは、これに対応したことで、Twitter(現:X)の「リポストをオフのする」機能のように"特定ユーザーのリポストをクライアント上で非表示にする"といったことができるようになりました。リアクションも同様に非表示にできます。 nostterでは、2024/07/29以降、ユーザーのプロフィール画面からこれらの設定を行えるようになっています。

2024/06/22 20時の時点では、nostter上ではこれを設定する画面が用意されていなかったので、別アプリを用いたり、イベントを自分で投げるなどして別途設定する必要がありました。 以下は、別アプリを用いて設定した際の手順です。
手順
kind:30007はのすとびうあというWebアプリで設定しました。 以下のようにのすとびうあのホーム画面「リストの種類」で30007を入力するか、

https://nostviewstr.vercel.app/<npub文字列>/30007にアクセスして設定画面にいけました^3。左下の方にある≡を押して

ポップアップの「編集」を押して

ここではリポストのミュートのため、IDの欄に対応するイベントの種類の番号である「6」を入れて

右下にある青いボタン押して

Userの欄にリポストをミュートするユーザーの公開鍵のnpub文字列を入れ、public(ミュート状況が公開される)あるいはprivate(非公開)のボタンを押したら

そのユーザーが追加されて設定完了!

この設定を行うことで、入力した公開鍵(ユーザー)のリポストをnostter上でもミュートできました🙌
リポストやリアクションがどのように表示されるかをユーザーがコントロールできると便利なので、今後いろんなクライアントで対応されればいいな〜と思います!
-
 @ f5194aa4:c08836bb
2024-11-08 17:07:07
@ f5194aa4:c08836bb
2024-11-08 17:07:07At Jewelry by Serendipity, we offer an exquisite collection of promise rings, each designed to symbolize love, commitment, and a shared future. Crafted with care from high-quality materials, our promise rings are perfect for celebrating a special relationship or marking an important milestone. From classic designs to contemporary styles, each ring reflects the unique bond it represents. Whether you're making a promise to a loved one or celebrating a friendship, our promise rings are a beautiful reminder of the meaningful connections in your life.
-
 @ 4c96d763:80c3ee30
2024-08-19 16:26:43
@ 4c96d763:80c3ee30
2024-08-19 16:26:43Changes
Rusty Russell (3):
- Makefile: fix missing dependencies on bolt11 headers.
- bolt11: update to latest version from CLN
- bolt11: remove unneeded fields.
William Casarin (1):
- ndb_filter_from_json
pushed to nostrdb:refs/heads/master
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-04 15:45:30
@ 5d4b6c8d:8a1c1ee3
2024-11-04 15:45:30The first moves of the Raiders bye-week adjustments have already happened. OC Luke Getsy, as well as their offensive line and quarterback coaches.
This had to happen, after the woeful offensive performances of the team. The run game especially has been abysmal and it's clearly due to coaching because the personnel is better than last year's o-line.
Getsy showed absolutely no ability to adapt to the defenses the team faced. His opening scripted plays often worked really well, but then the offense became completely stagnant for the remainder of the game.
It's not clear who will take over the play calling duties, or fill the other vacated roles, but the Raiders bloated coaching staff has three former play callers on it. The most likely candidate is Scott Turner.
This needs to be the first of several changes to the coaching staff. Situational game management has been atrocious, so the person filling that role needs to be relieved as well. Reports are that assistant head coach Marvin Lewis has been completely phoning it in, so he should be gone to.
The Raiders season has been over for a few weeks already and the remainder of the season needs to be about evaluating who to keep around. That should entail pairing down the largest coaching staff in the league, so we can see what Antonio Pierce does without the training wheels. This should also entail shutting down veterans like Minshew and Kolton Miller, in favor of getting a look at all the young guys on the roster.
originally posted at https://stacker.news/items/753300
-
 @ eac63075:b4988b48
2024-10-20 12:44:20
@ eac63075:b4988b48
2024-10-20 12:44:20Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.
Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.
The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.
Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.
The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
Conclusion of the Technical Debate
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.

Table reference: Patrick Breyer - Chat Control in 23 September 2024
Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.
The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
Conclusion of the Debate
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.
User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
Summary of Consequences
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.
The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.
Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ 57d1a264:69f1fee1
2024-11-04 15:17:28
@ 57d1a264:69f1fee1
2024-11-04 15:17:28——— NEW YORK (Nov. 4, 2024) — The Human Rights Foundation (HRF), along with partners dedicated to artistic freedom, expresses deep concern over the arrest and arbitrary detention of Gao Zhen, a prominent contemporary Chinese artist and a member of the well-known Gao Brothers, a collaborative artist duo. In a letter to the Consulate General of the People’s Republic of China in New York and other embassies, we call for his unconditional release.
On Aug. 26, Gao was arrested and detained after 30 police officers conducted a raid on his studio in Yanjiao, a town in the small city of Sanhe, in the northern province of Hebei. He has been held since at the Sanhe City Detention Center on charges of “slandering China’s heroes and martyrs” — a crime punishable by up to three years in prison.
A United States lawful permanent resident, Gao, 68, has made a career out of exposing the horrors of the Cultural Revolution through satirical humor that pushes the boundaries of social commentary. His works are also bold critiques of the Cultural Revolution and former Chinese Communist Party (CCP) leader Mao Zedong and his authoritarian rule of the country.
“These topics are sensitive and considered taboo in today’s CCP-controlled China, yet it is crucial to educate the world on the truth of Mao’s dictatorial legacy,” HRF Chief Advocacy Officer Roberto Gonzalez said. “Mr. Zhen’s detention is not only a violation of his basic rights but also an attack on the fundamental freedoms of all Chinese people, who have the right to learn the truth about dictator Mao Zedong.”
HRF demands Gao Zhen’s immediate and unconditional release as well as the CCP’s repeal of the Heroes and Martyrs Protection Law to safeguard artistic freedom in China.
For press inquiries, please contact media@hrf.org.
The Human Rights Foundation (HRF) is a nonpartisan nonprofit organization that promotes and protects human rights globally, with a focus on closed societies.
originally posted at https://stacker.news/items/753275
-
 @ d3052ca3:d84a170e
2024-11-08 14:46:09
@ d3052ca3:d84a170e
2024-11-08 14:46:09The shift of the American working class from the Democratic to the Republican Party in this last election, and the outrage it has generated among many leftist American academics, has led me to reflect on why so many academics become strong socialists or even communists, while the vast majority of the American “working class” do not.
They would likely call it “false consciousness” on the part of the American worker. By I see it as false consciousness among elites: they do not recognize that they are elites, and that their social status motivates them differently from how the typical American worker is motivated. In short, there is a difference between economic class (being a “worker”) and social status (being an “elite”). In this I am convinced that Peter Turchin’s structural-demographic theory continues to have explanatory power. (I won’t go into that here, but do check out his work.)
Socialism and even communism carry strong appeal for a specific kind of highly educated, young elite today: the kind that needs to work for a living, but still sees itself as elite. These are not “white collar workers;” they are “precarious elites.” They are subject to a dynamic that few want to talk about:
Some of the worst labor exploitation in this country occurs in so-called “prestige industries.” These include education (higher and lower), entertainment, journalism, publishing, art, philanthropy—even, on the higher-paid end, investment banking and other financial services.
You want to help a celebrity launch a new brand or product? Prepare to make $35,000 a year and work 24 hours a day, 7 days a week, doing countless frenzied tasks that have nothing to do with your job description.
You want to teach philosophy at a University? Get ready to make $17,500 a year, if you’re lucky. If you’re an international graduate student, your visa to stay in the U.S. is also completely contingent on your advisor’s approval; as a result, abuse is rampant.
You want to write for The Atlantic or The New Yorker? You can maybe get a few hundred bucks per article as a freelancer; $60K per year as a staff writer, if you’re lucky.
You want to become a powerful banker? You may start at $150K per year right out of college, but you will work 80-120 hours a week at the expense of everything else in your life, no telling how long—certainly for years. Your mental and even physical health are the price you pay for this “opportunity.”
These are the jobs that children of elites want. They want these jobs so much that they are willing to subject themselves to highly fragmented, authoritarian, and toxic work environments, with such high turnover, particularly of junior workers, that it’s socially a war of all against all. These jobs are different from working at a factory or an established company—there is a “musical chairs” dynamic, authority is exercised arbitrarily and chaotically, the job tasks can change daily and even moment to moment, most relationships are based on dominance/submission, and there is no “solidarity.” Employers believe it’s a “privilege” for anyone to have these jobs, and that therefore no one in them has the right to complain. Their refrain: “There are always 100 more candidates ready to take your place.”
In addition, there is the psychology of being an elite: you expect to be treated better by virtue of your education and social status, so it can be shameful to admit that you are being abused and might need to fight for better working conditions. Young elites may even want to organize and collectively bargain, but they don’t know how—they’ve been carried along by their social status in extremely authoritarian and chaotic environments and may never have really built anything with others over time.
For many young precarious elites, therefore, socialism becomes a kind of dream of not only of a good workplace but of a good society—one where they get what they believe is their “due.”
These “precarious elites” do see their exploitation as a structural problem, but they blame “capitalism” instead of the brute fact of supply and demand: there are just too many of them competing for the same few prestige jobs. While the American worker imagines a path to better pay and working conditions through organizing, the precarious elite sees no such path—because for them status is just as, if not more, important than pay and benefits, and that is something much harder to negotiate. Elites insist that they should be able to do exactly the (prestigious) jobs that they want to do. They are also educated enough to have read the socialist and communist literatures. That combination leads to the fantasy that the government could force their employers not only to pay them more and treat them with dignity—which in some cases it could, certainly—but also to guarantee these conditions in prestige jobs for everyone who wants them.
There likely is a legitimate case to be made that some of these prestige employers are violating labor laws and should be held accountable. In other cases, there are certainly opportunities to pass new laws prohibiting what amounts to indentured servitude. But actually enforcing these laws will only reveal what is already plain as day: that there are far fewer prestige jobs than there are elites who want them.
The double bind for elites is that the prospect of taking a “lower status” job—even one that pays a lot more, where workers are treated significantly better—is even worse than being a de facto slave with a prestigious role. This leads precarious elites to demand a magical solution: the state. The state must not only protect workers, but guarantee certain kinds of jobs at certain levels of pay and benefits for anyone who wants them. Needless to say, this demand can never be fulfilled, and the cycle of partisanship is then retrenched: precarious elites blame American workers for having the gall to vote and organize based on self-interest, rather than to crusade for an idyllic state of affairs that will not come.
Originally published on twitter https://x.com/NSmolenski/status/1854347409012203687
Reposted to nostr without permission. Sorry not sorry. <3 u Natalie!
-
 @ 0861144c:e68a1caf
2024-11-04 12:27:35
@ 0861144c:e68a1caf
2024-11-04 12:27:35These are the previous parts: Part 1|Part 2|Part 3|Part 4|Part 5| Part 6| Part 7| Part 8| Part 9
The papacy enters one of its darkest periods, not only marked by a series of medieval violence but also by the utter prostitution of power in scenarios so obscene that, by the time you finish reading, you may question the absolute sanctity of the pontificate.
-
Formosus [891-896] Consecrated as bishop by Nicholas [105]; he was a missionary whose main strength was encouraging Christians to combat paganism through letters. He supported the coronation of Arnulf of Carinthia, against the wishes of Charles the Bald (France), who had the favor of John VIII [107]; Guido of Spoleto was forced to crown his son Lambert as Emperor, while the Pope began talks with Arnulf. The Pope sought Arnulf's help to free Italy from the Spoletos.
-
Boniface VI [896] He suffered from gout when elected and died 15 days later.
-
Stephen VI [896-897] Elected with the support of the Emperor of the Holy Roman Empire and King of Italy, Lambert. This is one of the most shameful moments in the Church's history. In March 897, a posthumous trial was initiated against Formosus [111], during which Formosus' body was exhumed, dressed in papal vestments, given a defense lawyer, and put on trial. He was found guilty, his election as Pope invalidated, all his appointments and ordinations annulled, his body stripped of its vestments, and his remains thrown into the Tiber River. A few months later, following an earthquake, a mob took advantage of the chaos to assassinate the Pope, strangling him, presumably on the orders of the Spoletos in revenge for the trial known today as the Cadaver Synod or the Synod of Horror.
This is a representation of the Cadaver Synod. Too strong for me. Jean-Paul Laurens (1870)
-
Romanus [897] Seeing the chaos left by his predecessor, he began the process of rehabilitating Formosus [111] but died 90 days after assuming office. It is hypothesized that he was poisoned.
-
Theodore II [897] Held power for 20 days. His first order was to return Formosus' remains to St. Peter's Basilica and convened a synod that annulled all decisions from the Synod of Horror, declaring it void. Notably, Lambert of Spoleto's supporters wanted Count of Tusculum, Sergius, as Pope. Theodore was murdered, possibly by poisoning.
-
John IX [898-900] A Benedictine monk, elected with Lambert of Spoleto's support. He completed the work of his predecessor and, to avoid further violence, decreed that Papal Consecration must take place in the presence of the Emperor's representative. This reversed the Constitutio Lotharii. He also prohibited the tradition of looting bishops' palaces or papal palaces upon their death, declared Arnulf's consecration invalid, and granted all prerogatives to Lambert, his protector. The anti-Formosus faction wanted Sergius [119] as Pope but failed. The Theophylact family began tightening its grip on the papacy.
-
Benedict IV [900-903] Elected when the throne of the Holy Roman Empire was vacant. Lambert died in 899. Berengar I, King of Italy and grandson of Louis the Pious, claimed the imperial title, but the Pope granted it to Louis III the Blind, hoping he would defend against Hungarian invasions from the north and Saracens from the south. Louis was defeated by Berengar, blinded, and exiled. Lacking support, Benedict sought (a major error) support from the Theophylact family, including Theodora and her daughter Marozia, who would dominate the papacy henceforth.
-
Leo V [903] Elected Pope, little is known about his papacy. He was imprisoned and murdered 30 days after his election, likely by Pope Sergius III (his successor). Christopher the Priest declared himself Pope (antipope) but was also murdered, allegedly by Sergius III.
-
Sergius III [904-911] Linked to the Theophylact family and a supporter of the Synod of Horror, where he actively participated. He began the pornocracy[^1] period. He attempted to desecrate Formosus' tomb, without success. He married Alberic to Marozia, rumored to be the Pope's mistress. The Cluny Abbey was founded in 910 by William of Aquitaine and linked to the papal estate, initiating the Cluniac reform.
-
Anastasius III [911-913] Elected with the support of Theodora and Marozia. The second period of the pornocracy. A puppet of the Theophylact family. The conversion of the Normans began during his papacy.
-
Lando [913-914] Elected with Theodora and Marozia's support. The third period of the pornocracy. Nothing significant is recorded.
-
John X [914-928] Fiscal agent for the Archbishop of Ravenna. The fourth period of the pornocracy. Favored by Theodora, widow of Theophylact, with whom he had relations. His main role was leading an army for the first time in history, supported by Alberic, to defeat the Saracens at the Battle of Garigliano [916] and permanently expel them. Berengar I was assassinated in 924, the last Emperor of the Holy Roman Empire. John appointed the five-year-old Hugh of Vermandois as Archbishop of Reims. He was murdered by Marozia's henchmen for being useless to her family's interests.
-
Leo VI [928] The fifth period of the pornocracy. No significant events are recorded. He was murdered on Marozia's orders.
-
Stephen VII [928-931] The sixth period of the pornocracy. He was murdered on Marozia's orders.
-
John XI [931-935] The seventh and final period of the pornocracy. An illegitimate son of Marozia, reportedly fathered by Alberic, Duke of Spoleto. Became Pope at age 20. Marozia erred by marrying Hugh, King of Italy, prompting a rebellion by her eldest son from her first marriage, Alberic II. He imprisoned his mother with the Pope's and his half-brother's support. John granted Cluny Abbey the power to include monastic houses following their rules. Abbot Hugh rose to prominence and is considered one of the greats in history.
[^1]: Pornocracy is an Italian term meaning the government by courtesans or prostitutes. It first appeared in the writings of Cardinal Baronius, referring to a period in which two women wielded real power: Theodora, wife of the Roman senator Theophylact, and her daughter Marozia. This term has been used throughout history regardless of gender or sexual orientation.
originally posted at https://stacker.news/items/753048
-
-
 @ 0176967e:1e6f471e
2024-07-28 15:31:13
@ 0176967e:1e6f471e
2024-07-28 15:31:13Objavte, ako avatari a pseudonymné identity ovplyvňujú riadenie kryptokomunít a decentralizovaných organizácií (DAOs). V tejto prednáške sa zameriame na praktické fungovanie decentralizovaného rozhodovania, vytváranie a správu avatarových profilov, a ich rolu v online reputačných systémoch. Naučíte sa, ako si vytvoriť efektívny pseudonymný profil, zapojiť sa do rôznych krypto projektov a využiť svoje aktivity na zarábanie kryptomien. Preskúmame aj príklady úspešných projektov a stratégie, ktoré vám pomôžu zorientovať sa a uspieť v dynamickom svete decentralizovaných komunít.
-
 @ 9e69e420:d12360c2
2024-11-08 13:01:01
@ 9e69e420:d12360c2
2024-11-08 13:01:01City Commissioners’ Office Tells Non-Citizens They Can Vote if They Are Philly Residents; NGO ‘Ceiba’ Across the Street Sends Non-Citizen Voter with an ‘ITIN’
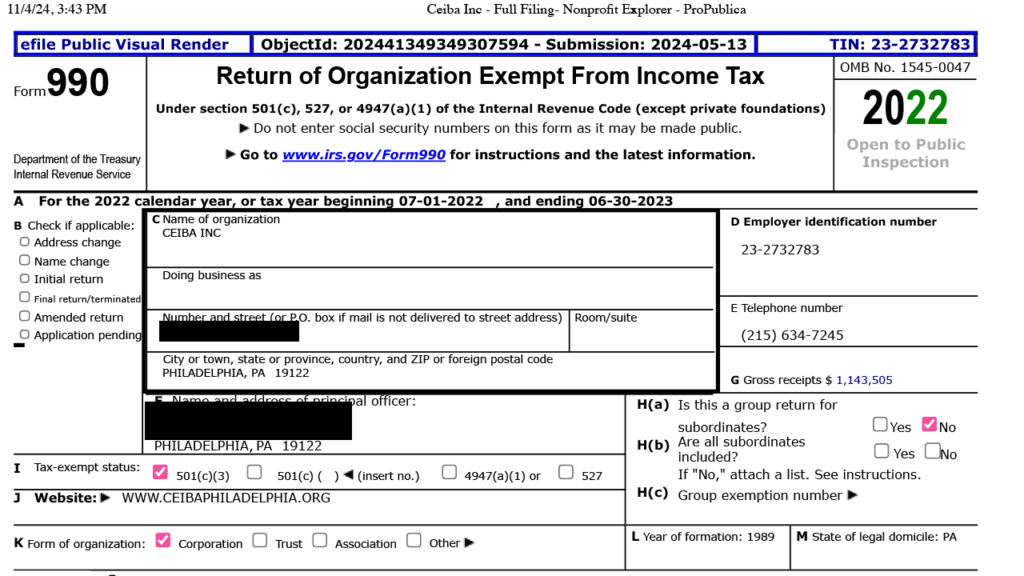
In a recent conversation, an undercover journalist from O’Keefe Media Group spoke with Milton Jamerson, an Election and Voter Registration Clerk at the Philadelphia City Commissioners Office.
During this exchange, Jamerson confirmed that non-citizens residing in Philadelphia could participate in local elections, raising questions about Philadelphia’s voting policies, particularly concerning the role of residency versus citizenship in voting eligibility.
Adding to the complexity, the organization Ceiba, a nongovernmental organization (NGO) located across the street, has also asserted that individuals with an Individual Taxpayer Identification Number (ITIN) are eligible to vote in local elections. However, the implications of Ceiba’s statement warrant careful consideration.
The Individual Taxpayer Identification Number (ITIN) is a nine-digit identifier issued by the IRS to people who are required to pay taxes but do not qualify for a Social Security Number, including non-citizens. It’s important to note that an ITIN serves only as a tax identifier and does not provide any form of legal voting rights or U.S. citizenship.
Saucesauce
naddr1qqgrjvpcxqmryefnxuer2e3excmnvq3qne57gg8xphmfek292yyg9nlyfkgh273vtrguy8qz0fuh05frvrpqxpqqqp65776qtuwPhiladelphia
-
 @ 0176967e:1e6f471e
2024-07-28 09:16:10
@ 0176967e:1e6f471e
2024-07-28 09:16:10Jan Kolčák pochádza zo stredného Slovenska a vystupuje pod umeleckým menom Deepologic. Hudbe sa venuje už viac než 10 rokov. Začínal ako DJ, ktorý s obľubou mixoval klubovú hudbu v štýloch deep-tech a afrohouse. Stále ho ťahalo tvoriť vlastnú hudbu, a preto sa začal vzdelávať v oblasti tvorby elektronickej hudby. Nakoniec vydal svoje prvé EP s názvom "Rezonancie". Učenie je pre neho celoživotný proces, a preto sa neustále zdokonaľuje v oblasti zvuku a kompozície, aby jeho skladby boli kvalitné na posluch aj v klube.
V roku 2023 si založil vlastnú značku EarsDeep Records, kde dáva príležitosť začínajúcim producentom. Jeho značku podporujú aj etablované mená slovenskej alternatívnej elektronickej scény. Jeho prioritou je sloboda a neškatulkovanie. Ako sa hovorí v jednej klasickej deephouseovej skladbe: "We are all equal in the house of deep." So slobodou ide ruka v ruke aj láska k novým technológiám, Bitcoinu a schopnosť udržať si v digitálnom svete prehľad, odstup a anonymitu.
V súčasnosti ďalej produkuje vlastnú hudbu, venuje sa DJingu a vedie podcast, kde zverejňuje svoje mixované sety. Na Lunarpunk festivale bude hrať DJ set tvorený vlastnou produkciou, ale aj skladby, ktoré sú blízke jeho srdcu.
Podcast Bandcamp Punk Nostr website alebo nprofile1qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qy88wumn8ghj7mn0wvhxcmmv9uq3xamnwvaz7tmsw4e8qmr9wpskwtn9wvhsz9thwden5te0wfjkccte9ejxzmt4wvhxjme0qyg8wumn8ghj7mn0wd68ytnddakj7qghwaehxw309aex2mrp0yh8qunfd4skctnwv46z7qpqguvns4ld8k2f3sugel055w7eq8zeewq7mp6w2stpnt6j75z60z3swy7h05
-
 @ 5d4b6c8d:8a1c1ee3
2024-11-04 02:05:22
@ 5d4b6c8d:8a1c1ee3
2024-11-04 02:05:22I just saw that Adam Silver is considering alternative formats for the NBA All-Star Game, in an effort to have something fans might actually enjoy watching. There are no details about what's under consideration, but this seems like a fun topic to speculate on.
Personally, I'd like to see the game replaced with a 3x3 tournament. The same 24 players could be assigned to 8 teams and play a three round tournament of short games.
I would also love a one on one tournament, but I know most of the best players would chicken out.
What say you?
originally posted at https://stacker.news/items/752728
-
 @ eac63075:b4988b48
2024-10-20 12:39:57
@ eac63075:b4988b48
2024-10-20 12:39:57Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.
Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.
The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.
Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.
The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
Conclusion of the Technical Debate
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.

Table reference: Patrick Breyer - Chat Control in 23 September 2024
Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.
The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
Conclusion of the Debate
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.
User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
Summary of Consequences
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.
The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.
Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ 68fa45dc:3d2a26ed
2024-11-08 10:59:23
@ 68fa45dc:3d2a26ed
2024-11-08 10:59:23Wie Unternehmen Anti-Spyware-Geräte-Störsender erfolgreich einsetzen können
Im modernen Geschäftsumfeld wird die Bedeutung von Informationssicherheit und Datenschutz immer wichtiger und die Bedrohungen, denen Unternehmen ausgesetzt sind, werden immer komplexer. Angesichts der rasanten Entwicklung der Technologie kommt es häufig zu Spionage- und Informationslecks, und Unternehmen müssen dringend wirksame Maßnahmen ergreifen, um ihre eigenen Interessen zu schützen. Unter vielen Schutzmethoden haben sich Anti-Spyware-Geräte Störsender Kaufen nach und nach zu einem wirksamen Werkzeug für Unternehmen zur Abwehr interner und externer Bedrohungen entwickelt. In diesem Artikel wird untersucht, wie Unternehmen Anti-Spyware-Geräte wie Mobiltelefon-Störsender, WLAN-Störsender, Anti-Tracking-Störsender und Kameradetektoren erfolgreich einsetzen können, um die Schutzfunktionen für die Informationssicherheit zu verbessern.
Anwendung des Handy-Störsender
Handy-Störsender blockieren Handysignale innerhalb bestimmter Frequenzen und verhindern so den Diebstahl von Informationen in Konferenzräumen oder sensiblen Bereichen. Unternehmen können beim Einsatz von Handy-Störsendern die folgenden Strategien in Betracht ziehen:
1. Identifizieren Sie sensible Bereiche: Zunächst sollten Unternehmen identifizieren, welche Bereiche sensibel sind, beispielsweise Vorstandssitzungsräume, Forschungs- und Entwicklungsabteilungen sowie Finanzabteilungen. Der Einsatz von Störsendern für Mobiltelefone an diesen Orten kann Abhören und Informationslecks wirksam verhindern.
2. Rechtmäßige und konforme Verwendung: Die Verwendung von handy störsender muss den örtlichen Gesetzen und Vorschriften entsprechen und sicherstellen, dass sie nur in zulässigen Situationen verwendet werden. Unternehmen sollten sich vorab über die einschlägigen Gesetze informieren und beim Einsatz von Störsendern Aufzeichnungen führen, um Rechtsstreitigkeiten vorzubeugen.
3. Bewerten Sie regelmäßig die Wirksamkeit: Unternehmen sollten die Wirksamkeit von Mobiltelefon-Störsendern regelmäßig bewerten, z. B. durch die Überwachung der Kommunikationssicherheit in Konferenzräumen und die unverzügliche Anpassung von Strategien nach Feststellung von Nichteinhaltung.
Anwendung des WIFI-Störsender
WLAN-Störsender können den illegalen Zugriff und die Überwachung von drahtlosen Unternehmensnetzwerken verhindern. Um WLAN-Störsender effektiv zu nutzen, können Unternehmen die folgenden Maßnahmen ergreifen:
1. Netzwerksicherheitsrichtlinie: Entwickeln Sie strenge Netzwerksicherheitsrichtlinien, verschlüsseln Sie das drahtlose Unternehmensnetzwerk, beschränken Sie den Zugriff auf Geräte und verwenden Sie WLAN-Störsender, um unbefugte Geräteverbindungen zu verhindern.
2. Dynamische Anpassung: Passen Sie die Verwendung des WiFi Jammer dynamisch an Änderungen in der Umgebung an. Verstehen Sie die umgebenden Netzwerkbedingungen und überprüfen Sie regelmäßig den Betriebsstatus des Störsenders, um sicherzustellen, dass er optimal funktioniert.
3. Mitarbeiterschulung: Bieten Sie Ihren Mitarbeitern Cybersicherheitsschulungen an, um ihr Bewusstsein für Cybersicherheitsbedrohungen zu schärfen. Machen Sie Ihren Mitarbeitern den Zweck und die Bedeutung von Störsendern klar, um ihr Sicherheitsbewusstsein zu stärken.
Verwendung von Anti-Tracking-Störsendern
Anti-Tracking-Störsender werden verwendet, um potenzielle Tracking-Geräte zu blockieren und die Geschäftsleitung und wichtige Informationen zu schützen. Unternehmen können beim Einsatz von Anti-Tracking-Störsendern Folgendes berücksichtigen:
1. Identifizierung von Personen mit hohem Risiko: Identifizieren Sie Führungskräfte oder wichtige Mitarbeiter, die besonderen Schutz benötigen, damit Anti-Tracking-GPS Jammer richtig konfiguriert werden können, wenn sie reisen oder wichtige Aktivitäten durchführen.
2. Jederzeit überwachen: Unternehmen sollten mit Geräten ausgestattet sein, die das Tracking-Verhalten in Echtzeit überwachen können, und diese in Kombination mit Anti-Tracking-Störsendern verwenden, um sicherzustellen, dass keine potenziellen Risiken übersehen werden.
3. Notfallplan: Entwickeln Sie einen detaillierten Notfallplan für den Umgang mit möglichen Tracking-Vorfällen. Sobald eine ungewöhnliche Situation entdeckt wird, kann schnell ein Plan zur Bewältigung dieser Situation auf den Weg gebracht werden.
Die Rolle von Kameradetektoren
Kameradetektoren spielen eine wichtige Rolle bei der Identifizierung versteckter Kamerageräte für Unternehmen, insbesondere bei Konferenzen und Geschäftsveranstaltungen. Unternehmen sollten Kameradetektoren effektiv einsetzen, um die Sicherheit und Privatsphäre von Meetings zu gewährleisten:
1. Regelmäßige Inspektion: Führen Sie vor wichtigen Ereignissen oder Besprechungen mithilfe von Kameradetektoren umfassende Inspektionen durch, um sicherzustellen, dass die Besprechungsumgebung nicht durch illegale Überwachungsgeräte beeinträchtigt wird.
2. Verwendungsspezifikationen entwickeln: Erstellen Sie beim Einsatz von Kamera Detektor detaillierte Bedienungsanleitungen und Spezifikationen, damit die Mitarbeiter die Verwendung und den Umfang der Detektionsausrüstung verstehen können.
3. Vertraulichkeitsschulung: Für Mitarbeiter, die an Geheimnissen beteiligt sind, wird eine Vertraulichkeitsschulung angeboten, damit sie die Gefahren versteckter Kameraausrüstung verstehen, ihre Wachsamkeit erhöhen und die Informationssicherheit schützen können.
Zusammenfassen
Mit der Verschärfung des geschäftlichen Wettbewerbs und der Entwicklung der Informationstechnologie nehmen die Sicherheitsrisiken für Unternehmen weiter zu. Durch den sinnvollen Einsatz von Anti-Spyware-Geräten wie Mobiltelefon-Störsendern, WLAN-Störsendern, Anti-Tracking-Störsendern und Kameradetektoren können Unternehmen nicht nur Informationslecks und Spionage wirksam verhindern, sondern auch das allgemeine Sicherheitsmanagementniveau verbessern. Wenn Unternehmen diese Geräte verwenden, müssen sie jedoch Gesetze und Vorschriften einhalten, die Datenschutzrechte von Mitarbeitern und Kunden respektieren und den Schutz der Informationssicherheit innerhalb eines rechtlichen und konformen Rahmens gewährleisten. Nur so können wir im harten Wettbewerb auf dem Markt unbesiegbar bleiben.
-
 @ 0176967e:1e6f471e
2024-07-27 11:10:06
@ 0176967e:1e6f471e
2024-07-27 11:10:06Workshop je zameraný pre všetkých, ktorí sa potýkajú s vysvetľovaním Bitcoinu svojej rodine, kamarátom, partnerom alebo kolegom. Pri námietkach z druhej strany väčšinou ideme do protiútoku a snažíme sa vytiahnuť tie najlepšie argumenty. Na tomto workshope vás naučím nový prístup k zvládaniu námietok a vyskúšate si ho aj v praxi. Know-how je aplikovateľné nie len na komunikáciu Bitcoinu ale aj pre zlepšenie vzťahov, pri výchove detí a celkovo pre lepší osobný život.
-
 @ fd208ee8:0fd927c1
2024-11-03 21:51:39
@ fd208ee8:0fd927c1
2024-11-03 21:51:39All memed out
It finally happened. I think it was October 25th, at circa 18:45 in the evening. I was doomscrolling my Nostr feed, and kept seeing the same Bitcoin memes repeated over and over, by different people. They weren't even reposts, they were copy-pasted versions of the same image. A very funny image. Well, it was very funny last year... and the year before that... and probably the year before that, when it appeared on a different network.
Because it's all just reposts, copy-pastes and rehashes of the Best of Bitcoin Twitter, just like the tiresome influencers, with their groupies and their Episode 498 of Let's all eat a large chunk of lightly-burnt dead animal and count our stacks before jetting off to talk about how to save the poors by getting them to buy individual satoshis with money they don't have.

I'm the poors your looking for
It's all so tiresome. It has little bearing on the real world I see around me, where most people are thinking all day about 99 problems and Bitcoin ain't one.
Which is, of course, what the Bitcoin influencers would have you believe, is the reason that they're poor. What in the world could be more important, than thinking about Bitcoin? Why do these people not get with the program? Don't they know, that we are trying to save them?
Why are they worrying about OtherProblems? Don't they know that all OtherProblems can be fixed with Bitcoin? Really, if you just go back far enough, in any current, situational problem, you will discover that there was some slight, negative shift to the history record that involved soft money. It's the financial version of the Butterfly Effect.
That's why #BitcoinFixesThis. Bitcoin fixes everything, if you just think about it, for long enough.
The same way that we all actually come out of Africa, supposedly, if you go back enough generations. So, coming out of Africa, now, as a Real Life Person in The Present is supposed to have no significance. What does someone from Cameroon know about Africa, that someone from Alaska doesn't? Both people come out of Africa, if you just think about it, for long enough.

And maybe that really is true. Maybe Bitcoin will eventually end all vice and crimes, save the planet, and we will all just hold hands and sing kumbaya all day, while waiting for the Singularity to upload us to Satoshi.
Bitcoin envelope budgeting
Or maybe it's not. Maybe it's just a really hard, digital money that incentivizes savings, functions as a reliable measure, and makes micropayments possible on a global scale. Those really are things that will help the poors, including myself. I can see it, already, when trying to organize pre-paid meetups or figure out what to do with our household's meager savings, when the stock market is looking particularly bubblicious.

But this is what I would consider Boring Bitcoin. Bitcoin home economics. Penny-pinching Bitcoin. Bitcoin for homemakers. How to use the Bitcoin envelope budgeting system to beat inflation by a margin of 13%.
The actual use of Bitcoin as money, rather than as a mere investment gamble or hype machine. That's the part of Bitcoin that nobody seems to really talk about because it's incredibly practical, dull, and useful, and it can only be tested by -- Oh, the horror! -- actually spending Bitcoin.
But... perhaps I will begin talking about it. Perhaps those of us, Bitcoiners, who are having fun staying poor, while stacking sats, should speak up a bit more. Perhaps the boring stuff is actually the interesting stuff. Perhaps there is more to say about Bitcoin, than can fit into a meme.
