-
 @ f9cf4e94:96abc355
2024-12-31 20:18:59
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( dominictarr ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt (ssb) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( fonte )
Dominic descobriu o termo boato em um artigo de pesquisa que leu.
Em sistemas distribuídos, fofocar é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto. Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar. Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário de bordo (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. Cada item adicionado a um log do usuário é chamado de mensagem.
Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor ssb ), mas também é conhecido como “Scuttlebot” e
sbotna linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
Pubs - Hubs
Pubs públicos
| Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | |
scuttle.us| @Ryan |scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=| | pub1.upsocial.com | @freedomrules |pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=| | Monero Pub | @Denis |xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=| | FreeSocial | @Jarland |pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=| |ssb.vpn.net.br| @coffeverton |ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=| | gossip.noisebridge.info | Noisebridge Hackerspace @james.network |gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=|Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | |
many.butt.nz| @dinosaur | mikey@enspiral.com | |one.butt.nz| @dinosaur | mikey@enspiral.com | |ssb.mikey.nz| @dinosaur | mikey@enspiral.com | | ssb.celehner.com | @cel | cel@celehner.com |Pubs muito grandes
Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)
| Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | |
scuttlebutt.de| SolSoCoG |scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=| |Lohn's Pub| @lohn |p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=| | Scuttle Space | @guil-dot | Visit scuttle.space | |SSB PeerNet US-East| timjrobinson |us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=| | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |GUI - Interface Gráfica do Utilizador(Usuário)
Patchwork - Uma GUI SSB (Descontinuado)
Patchwork é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: scuttlebutt.nz
Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub. Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que Patchwork e Patchfoo , então você pode facilmente dar uma volta com sua identidade existente.

Planetary - GUI para IOS

Planetary é um app com pubs pré-carregados para facilitar integração.
Manyverse - GUI para Android

Manyverse é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
Fontes
-
https://scuttlebot.io/
-
https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
-
https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
-
Secure Scuttlebutt : um protocolo de banco de dados global.
-
-
 @ 6be5cc06:5259daf0
2024-12-29 19:54:14
@ 6be5cc06:5259daf0
2024-12-29 19:54:14Um dos padrões mais bem estabelecidos ao medir a opinião pública é que cada geração tende a seguir um caminho semelhante em termos de política e ideologia geral. Seus membros compartilham das mesmas experiências formativas, atingem os marcos importantes da vida ao mesmo tempo e convivem nos mesmos espaços. Então, como devemos entender os relatórios que mostram que a Geração Z é hiperprogressista em certos assuntos, mas surpreendentemente conservadora em outros?
A resposta, nas palavras de Alice Evans, pesquisadora visitante na Universidade de Stanford e uma das principais estudiosas do tema, é que os jovens de hoje estão passando por um grande divergência de gênero, com as jovens mulheres do primeiro grupo e os jovens homens do segundo. A Geração Z representa duas gerações, e não apenas uma.
Em países de todos os continentes, surgiu um distanciamento ideológico entre jovens homens e mulheres. Milhões de pessoas que compartilham das mesmas cidades, locais de trabalho, salas de aula e até casas, não veem mais as coisas da mesma maneira.
Nos Estados Unidos, os dados da Gallup mostram que, após décadas em que os sexos estavam distribuídos de forma relativamente equilibrada entre visões políticas liberais e conservadoras, as mulheres entre 18 e 30 anos são agora 30 pontos percentuais mais liberais do que os homens dessa faixa etária. Essa diferença surgiu em apenas seis anos.
A Alemanha também apresenta um distanciamento de 30 pontos entre homens jovens conservadores e mulheres jovens progressistas, e no Reino Unido, a diferença é de 25 pontos. Na Polônia, no ano passado, quase metade dos homens entre 18 e 21 anos apoiou o partido de extrema direita Confederation, em contraste com apenas um sexto das jovens mulheres dessa mesma idade.
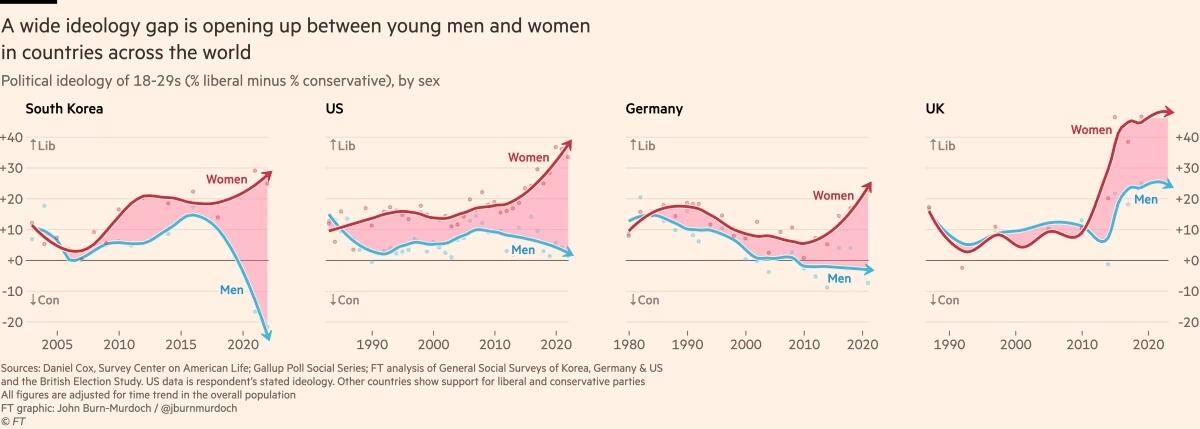
Fora do Ocidente, há divisões ainda mais acentuadas. Na Coreia do Sul, há um enorme abismo entre homens e mulheres jovens, e a situação é semelhante na China. Na África, a Tunísia apresenta o mesmo padrão. Vale notar que em todos os países essa divisão drástica ocorre principalmente entre a geração mais jovem, sendo muito menos pronunciada entre homens e mulheres na faixa dos 30 anos ou mais velhos.
O movimento # MeToo foi o principal estopim, trazendo à tona valores feministas intensos entre jovens mulheres que se sentiram empoderadas para denunciar injustiças de longa data. Esse estopim encontrou especialmente terreno fértil na Coreia do Sul, onde a desigualdade de gênero é bastante visível e a misoginia explícita é comum. (palavras da Financial Times, eu só traduzi)
Na eleição presidencial da Coreia do Sul em 2022, enquanto homens e mulheres mais velhos votaram de forma unificada, os jovens homens apoiaram fortemente o partido de direita People Power, enquanto as jovens mulheres apoiaram o partido liberal Democratic em números quase iguais e opostos.
A situação na Coreia é extrema, mas serve como um alerta para outros países sobre o que pode acontecer quando jovens homens e mulheres se distanciam. A sociedade está dividida, a taxa de casamento despencou e a taxa de natalidade caiu drasticamente, chegando a 0,78 filhos por mulher em 2022, o menor número no mundo todo.
Sete anos após a explosão inicial do movimento # MeToo, a divergência de gênero em atitudes tornou-se autossustentável.
Dados das pesquisas mostram que em muitos países, as diferenças ideológicas vão além dessa questão específica. A divisão progressista-conservadora sobre assédio sexual parece ter causado ou pelo menos faz parte de um alinhamento mais amplo, em que jovens homens e mulheres estão se organizando em grupos conservadores e liberais em outros assuntos.
Nos EUA, Reino Unido e Alemanha, as jovens mulheres agora adotam posturas mais liberais sobre temas como imigração e justiça racial, enquanto grupos etários mais velhos permanecem equilibrados. A tendência na maioria dos países tem sido de mulheres se inclinando mais para a esquerda, enquanto os homens permanecem estáveis. No entanto, há sinais de que os jovens homens estão se movendo para a direita na Alemanha, tornando-se mais críticos em relação à imigração e se aproximando do partido de extrema direita AfD nos últimos anos.
Seria fácil dizer que tudo isso é apenas uma fase passageira, mas os abismos ideológicos apenas crescem, e os dados mostram que as experiências políticas formativas das pessoas são difíceis de mudar. Tudo isso é agravado pelo fato de que o aumento dos smartphones e das redes sociais faz com que os jovens homens e mulheres agora vivam em espaços separados e tenham culturas distintas.
As opiniões dos jovens frequentemente são ignoradas devido à baixa participação política, mas essa mudança pode deixar consequências duradouras, impactando muito mais do que apenas os resultados das eleições.
Retirado de: https://www.ft.com/content/29fd9b5c-2f35-41bf-9d4c-994db4e12998
-
 @ 6f3670d9:03f04036
2024-12-29 08:20:22
@ 6f3670d9:03f04036
2024-12-29 08:20:22Disclaimer: - This will void your warranty - There might be differences between the Bitaxe and the Lucky Miner that might not cause issues or damage immediately, but might manifest long-term - Proceed at your own risk
A Different Pickaxe
You live in a place where it's difficult to get a Bitaxe. You have access to AliExpress. You look around. You find something called the "Lucky Miner LV06". A Bitaxe clone that uses the same mining chip as the Bitaxe Ultra (BM1366 ASIC). You buy one.
You plug it in, you enter your wallet address and other settings, and it starts mining. It works! Great!
But it's running a customized firmware. It's not AxeOS. Maybe there's something shady in the stock firmware. It's not open-source, after all. Also, AxeOS looks amazing... And that automatic pool fail-over feature is handy.
You think to yourself: "Maybe I can use the Bitaxe firmware on this?". Guess what? You're right!
Flashing From Web UI
What usually works for me is to: - Download the Bitaxe firmware files (
esp-miner.binandwww.bin) from GitHub (here). Version 2.4.1 seems to work well, as of this writing. - Then from the Lucky Miner web interface, upload the "Website" (www.bin) file. - Wait for a minute or two after it's done uploading. - Upload the "Firmware" (esp-miner.bin) file. - Wait another minute or two. - Unplug the power and plug it back in. - Set the "Core Voltage" and "Frequency" to the defaults. - Unplug the power and plug it back in again.If you're lucky (no pun intended), you'll have a working Lucky Miner with AxeOS. Update the settings and mine away!
However, often times I've been unlucky, like what happened while I was writing this article, ironically. The miner malfunctions for no obvious reason. It keeps rebooting, or it's not mining (zero/low hashrate), or the web interface is inaccessible. You name it.
The miner has become a "brick". How do you "unbrick" it?
When you brick a Bitaxe, you can recover it by flashing (uploading) a "Factory Image". The Bitaxe has a USB port that makes this easy. Follow the guide and it should come back to life again. Unfortunately, the Lucky Miner LV06 doesn't have a USB port. It has a serial port, though. We'll have to get our hands a bit dirty.
Flashing Using the Serial Port
We need to connect the serial port of the miner to a computer and run a program to flash (upload) the firmware file on the miner. Any 3.3v UART serial port should be sufficient. Unfortunately, PCs don't usually come with a UART serial port these days, let alone a 3.3v one. The serial port common in old computers is an RS-232 port, which will most probably fry your miner if you try to connect it directly. Beware.
In my case, as a serial port for my PC, I'm using an Arduino Due I had lying around. We connect it to the PC through USB, and on the other side we connect a few wires to the miner, which gives the PC access to the miner.
WARNING: Make sure your serial port is 3.3v or you will probably kill the miner. Arduino Uno is 5v not 3.3v, for example, and cannot be used for this.
Wiring
First, we need to open the Lucky Miner. Use a small flat screwdriver to gently push the two plastic clips shown in the picture below. Gently pry the top cover away from the bottom cover on the clips side first, then remove the other side. Be careful not to break the display cable.
Once the cover is off, you can find the miner's serial port in the top right corner (J10), as shown in the next picture. We'll also need the reset button (EN).
There are three screws holding the PCB and the bottom cover together. If you're confident in your ability to push the small button on the underside of the PCB with the bottom cover on, then no need to remove these. The following picture shows what we need from that side.
And the next picture shows the pins and USB port we will use from the Arduino.
Now, we need to connect: - The USB port on the Arduino labelled "programming" to the PC - Pin 18 (TX1) on the Arduino to J10 through-hole pad 5 (blue dot) - Pin 19 (RX1) on the Arduino to J10 through-hole pad 3 (green dot) - Any GND pin on the Arduino to J10 through-hole pad 4 (yellow dot)
I didn't need to solder the wires to the pads. Keeping everything stable, perhaps by putting a weight on the wires or a bit of tape, was sufficient in all my attempts.
Setting up the Arduino
To use the Arduino as a serial port for our PC, we'll have to make it pass-through data back and forth between the USB port and UART1, where we connected the miner.
The following steps are all done on a PC running Debian Linux (Bookworm), in the spirit of freedom and open-source.
First, we start the Arduino IDE. If the package for the Arduino Due board is not already installed, you'll see a small prompt at the bottom. Click "Install this package".
Click the "Install" button.
Once the package is installed, click "Close".
Next, we select the Due board. Click the "Tools" menu, select "Board", select "Arduino ARM (32-bits) Boards" and click "Arduino Due (Programming Port)"
Next, we select the port. Click the "Tools" menu again, select "Port", and click the port where the Arduino is connected. In my case it was "/dev/ttyACM0".
Now we need to upload the following code to the Arduino board. The code is actually the "SerialPassthrough" example from the IDE, but with the serial speed changed to match the miner.
``` void setup() { Serial.begin(115200); Serial1.begin(115200); }
void loop() { if (Serial.available()) { // If anything comes in Serial (USB), Serial1.write(Serial.read()); // read it and send it out Serial1 }
if (Serial1.available()) { // If anything comes in Serial1 Serial.write(Serial1.read()); // read it and send it out Serial (USB) } } ```
Copy/paste the code into the IDE and click upload. You'll see "Done uploading" at the bottom.
Next we'll test if we're receiving data from the miner. We start by opening the "Serial Monitor" from the "Tools" menu in the IDE. Then we change the baudrate to 115200.
Set the Arduino and the miner in a comfortable position, make sure the wires are held in place and got a good contact on both sides, and the power is plugged in.
Now we'll put the miner in "download" mode. Press and hold the button on the underside (K1), press and release the reset button (EN), then release the other button (K1).
You should see some text from the miner in the serial monitor window, like in the picture below.
Congratulations! We know we're able to receive data from the miner now. We're not sure transmit is working, but we'll find out when we try to flash.
Flashing Using the Serial Port, for Real
To flash the Lucky Miner we'll need a software tool named esptool and the factory image firmware file.
I usually use "esp-miner-factory-205-v2.1.8.bin" for the factory image (this one) as a base, and then flash the version I want from the Web UI, using the steps I mentioned earlier.
For esptool, the documentation (here) shows us how to install it. To make things a little easier on our Debian Linux system, we'll use pipx instead of pip. The instructions below are adapted for that.
First we make sure pipx is installed. Run this command in a terminal and follow the instructions:
sudo apt-get install pipxThen we install esptool using pipx. Run the following in a terminal:
pipx install esptoolThe output will be something like this:
user@pc:~$ pipx install esptool installed package esptool 4.8.1, installed using Python 3.11.2 These apps are now globally available - esp_rfc2217_server.py - espefuse.py - espsecure.py - esptool.py ⚠️ Note: '/home/user/.local/bin' is not on your PATH environment variable. These apps will not be globally accessible until your PATH is updated. Run `pipx ensurepath` to automatically add it, or manually modify your PATH in your shell's config file (i.e. ~/.bashrc). done! ✨ 🌟 ✨We can see pipx telling us we won't be able to run our tool because the folder where it was installed is not in the PATH variable. To fix that, we can follow pipx instructions and run:
pipx ensurepathAnd we'll see something like this:
``` user@pc:~$ pipx ensurepath Success! Added /home/user/.local/bin to the PATH environment variable.
Consider adding shell completions for pipx. Run 'pipx completions' for instructions.
You will need to open a new terminal or re-login for the PATH changes to take effect.
Otherwise pipx is ready to go! ✨ 🌟 ✨ ```
Now, close the terminal and re-open it so that esptool becomes available.
Finally, to actually flash the miner, put the miner in download mode, then in the following command change the port ("/dev/ttyACM0") to your serial port, as we've seen earlier, and the file path to where your firmware file is, and run it:
esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.binIf everything went fine, the tool will take a few minutes to flash the firmware to the miner. You'll see something like this in the output:
``` user@pc:~$ esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.bin esptool.py v4.8.1 Serial port /dev/ttyACM0 Connecting..... Detecting chip type... ESP32-S3 Chip is ESP32-S3 (QFN56) (revision v0.2) Features: WiFi, BLE, Embedded PSRAM 8MB (AP_3v3) Crystal is 40MHz MAC: 3c:84:27:ba:be:01 Uploading stub... Running stub... Stub running... Configuring flash size... Erasing flash (this may take a while)... Chip erase completed successfully in 9.5s Compressed 15802368 bytes to 1320190... Wrote 15802368 bytes (1320190 compressed) at 0x00000000 in 152.1 seconds (effective 831.2 kbit/s)... Hash of data verified.
Leaving... Hard resetting via RTS pin... ```
And we're done! Hopefully the miner will be recovered now.
Hope this helps!
Stay humble,
dumb-packageA Warning About Beta Versions of AxeOS
For reasons unknown to me, while I was writing this article I wanted to try the testing version of AxeOS, which was v2.4.1b (beta). Flashing from Web UI went smooth, but the miner stopped mining. I flashed back to v2.1.8 using the serial port, a known good version for me, but it wouldn't mine, still.
Thankfully, v2.4.1 was released recently, and flashing it from the Web UI magically revived my miner. So, be warned.
Bonus: File Hashes
For convenience, these are the SHA256 hashes of the files I used in this article: ``` da24fceb246f3b8b4dd94e5143f17bd38e46e5285e807ebd51627cb08f665c0a ESP-Miner-v2.4.1/esp-miner.bin 16c5c671391f0e3e88a3e79ce33fad3b0ec232b8572fad5e1e0d1ad3251ab394 ESP-Miner-v2.4.1/www.bin
d5182a15b6fa21d7b9b31bff2026d30afed9d769781a48db914730a5751e20c6 esp-miner-factory-205-v2.1.8.bin ```
-
 @ f4bf1fb5:b428f8d5
2025-01-02 23:44:03
@ f4bf1fb5:b428f8d5
2025-01-02 23:44:03DEG Mods is using a new piece of technology, specifically a new communications protocol that's censorship-resistant called NOSTR, and as such, it uses a non-traditional means of creating an account, as well as how you sign into sites that uses such new tech, like DEG Mods.
Since this is new to most people, it can be somewhat daunting, scary, suspicious, as with anything new, especially something where the individual holds sole responsibility of what they created, as there would be nobody to help them, in the case of creating an account, retrieve their account if it gets lost or if it gets compromised.
We'll skip on explaining in proper detail what NOSTR is specifically, and go straight ahead and explain the direct process of how to create an account, and how to sign in.
How to create an account on DEG Mods
Creating a DEG Mods account is creating a NOSTR account, and that can be done in multiple ways, from using a browser extension, to using a mobile app, to generating it directly on the site.
For the purposes of this current guide, and for the current version of DEG Mods, we'll only be guiding you on how to create a DEG Mods/NOSTR account using a browser extension. With that said, there are currently multiple ones that has been developed for this specific purpose. Some with more features than others, or some with a better UI/UX. For now, we'll be recommending you to install one called Nostr Connect (Chrome / FireFox)
Once you have installed that extension on your preferred browser, make sure that you have the extension pinned on your browser (for easy access and use). To do that, you'd have to open the quick extension preview window on your browser (for example, on Chrome or Brave, that'd be the puzzle-piece icon) and then click the pin icon next to the extension you want to pin. In this case, that'd be the Nostr Connect extension.
Now, click on the Nostr Connect extension icon and then click the gear icon, which will open a new tab/page to start the account creation process.
It's pretty straight forward from there. Just click on the "Generate" button then the save button. This will generate for you a pair of keys/addresses. The shown one is your private key (think of it as your password) that starts with 'nsec', which you should keep safe somewhere (like on a password manager), because if you lose it then you won't be able to access your account, or if it gets leaked then everyone would be able to access your account, and we won't be able to help you retrieve your private key/address or reset it to something else. You are the sole responsible person for your account's security.
Once you're done, close that page then click on the extension icon again. It will now show you your public key/address (think of this as your user ID).
How to sign into DEG Mods
Once you have the DEG Mods site open, click the 'Login' button at the top right. A popup will appear with an option to login with an extension. Click that and another popup will appear (this is your extension being triggered) asking you to authorize the login. Tick the box to remember this action if you'd like (for convenience) and click authorize.
Done. You've now created an account and logged into the site. Now you can publish game mods, comment on posts/pages, react, and more.
Video guide
If you don't feel like reading, or rather, if you're more comfortable watching a video guide on how to do all of this, then here's that video.
Questions and answers
Is this safe?
As we did not create these browser extensions or mobile apps, we can't necessarily guarantee anything, however, until proven otherwise, the browser extensions or mobile apps we recommended here are safe. If you're a programmer, you can check their code directly to see if there's anything suspicious, as they are open source.
Why do you have such a complicated way to make an account?
We understand that this may seem complicated, but it isn't if you think about it.
What did you actually do? You installed a browser extension, generated an account (a key pair), and signed in with a click of a single button. Install, generate, login.
It seems complicated because its something you haven't done before and outside of what you're used it, but in reality, it's actually a lot simpler than traditional methods, which involves creating an email address, then creating an account on each site you want to visit. With this, it's a one time event and you can log into DEG Mods, or any other site or app that's built ontop of NOSTR, with that same account, which holds all of your profile data and posts.
Why don't you have a normal way to make an account on DEG Mods?
Since DEG Mods is a truly censorship-resistant mods site, building the site on NOSTR was the ideal choice to make, which resulted in giving you, the user, the mod creator, and the mod enjoyer, the power of controlling your content, your posts, your profile, your account. We can't ban you because you have a NOSTR account, nor can we take down your posts/pages.
If we had made it so that you can use the normal way of making an account, where you have an email and password combo, then we can do all of those ban things. We would have the power to censor you. You'd have zero power, and we didn't want that outcome.
What do you mean you can't help me restore my account or reset my password?
The account you created was, because of the tech being used, created on your device, and not on any server that we control. As such, we don't see or save your account data (we don't know your private key/address, and we shouldn't). You also cannot change the private key/address of your account, as there is no way to do so / this is how the tech was developed.
Will you maintain and update this guide as time move forwards?
Yes. Since its in our interest to have more users on DEG Mods, we'll be updating this post so that it'll continue being useful to new users.
Can't you make a browser extension or app specifically for DEG Mods?
While it is possible, and we are interested in doing so, as to keep it always up to date and add more features, have the best UI/UX possible, etc, it would require us to receive funds and allocate it for this specific development. So the answer to this question is: If we're successful enough to have the funds to develop it.
Why can't I log into DEG Mods on my mobile phone?
You would need a NOSTR mobile signer for that, and we'll also need to implement such a feature to tell the site that you have that app. It'll come with time, and I'd say sooner rather than later.
-
 @ 6f3670d9:03f04036
2024-12-29 06:51:25
@ 6f3670d9:03f04036
2024-12-29 06:51:25This is my first long-form post. The starting line.
There's nothing of value here. Just using this as a marker.
I hope to post a lot more. Documenting how I made something work would be very useful to me, and hopefully others, but I've been too lazy to do that. Wish me luck!
Stay humble,
dumb-package -
 @ 6bae33c8:607272e8
2025-01-02 22:23:01
@ 6bae33c8:607272e8
2025-01-02 22:23:01I went 2-3 last week, which only matters bercause I was 5-0 in Week 16, and I thought I might have finished with an epic run, but it was not to be. Week 18 is always fun to guess who’s trying and who’s packing it in. My MO is usually to bet the teams who are missing the playoffs, have nothing to play for, but also no reason not to go all out. They’re usually undervalued.
Browns at Ravens — The Ravens need this game to win the division, so I expect them to try, though they might pull their starters in the second half if they’re way up. I’ll say Browns +14.5 and probably lay the wood.
Bengals at Steelers — The Bengals have a long shot chance of making the playoffs and will go all out. The Steelers are playing for the three seed, but they’d need the Browns to beat the Ravens. Hard to say whether they’ll go all out, but I’ll make it Bengals -3.
Panthers at Falcons — The Falcons need this (but also a Bucs loss), and the Panthers will go all out because they have no reason not to. I’ll say Panthers +4.5.
Killer Redskins at Cowboys — The KRs can move between the sixth and seventh seeds, but I doubt they’ll leave their starters in long. I’ll say KRs +6.5.
Bears at Packers — The Packers can move between the sixth and seventh seeds, but it doesn’t matter much. I’ll make it Bears -3.5.
Jaguars at Colts — Both teams are playing for nothing. Mac Jones is playing decently, and it’s unclear who’s under center for the Colts. I’ll say Jaguars +3.5.
Bills at Patriots — It’ll be Mitch Trubisky against maybe Drake Maye. The Bills don’t need it. I’ll say Bills +5.5.
Giants at Eagles — Neither team needs it, the Eagles are probably resting Saquon Barkley who has a chance to break the single-season rushing record against his old team that decided not to pay him. I’ll make it Giants -2.5.
Saints at Buccaneers — The Bucs need this, the Saints are a destroyed team. Maybe Derek Carr plays, but I’d be surprised. I’ll say Saints +14.5.
Texans at Titans — The Texans don’t care, the Titans can try their hardest. I’ll make it Texans +4.5.
49ers at Cardinals — Two failed teams playing out the string. I’ll say pick ‘em and probably stay away.
Chiefs at Broncos — The Chiefs are resting everyone, the Broncos need to win in order to get in. I’ll make it Chiefs +8.
Seahawks at Rams — The Rams have clinched, can only toggle between the third and fourth seeds. I’ll say Seahawks -6.
Chargers at Raiders — The Chargers can only toggle between the fifth and sixth seeds, the Raiders are obviously done. Let’s say Chargers +6.5.
Dolphins at Jets — Tua’s probably not playing, but the Dolphins still have an outside chance at the playoffs. I’ll make it a pick ‘em and lean Dolphins.
Vikings at Lions — This is for the No. 1 seed and a bye in the NFC. I’ll say Vikings +2.5 and lean Vikings due to their defense.
-
 @ 22c5769e:09af4623
2025-01-02 22:12:04
@ 22c5769e:09af4623
2025-01-02 22:12:04I can't wait to start something small with my dream goal to which is to start my own food truck by starting something small by selling eggroll. My passion is cooking, I love to learn new recipe and create my own recipe. My family& friends loves my cooking.
-
 @ e968e50b:db2a803a
2025-01-02 21:45:49
@ e968e50b:db2a803a
2025-01-02 21:45:49I checked, and it was 25,635 sats. I'm sure it's just a publicity stunt to inspire posts like this...but hey...I'm not above being duped into that type of marketing. Happy New Year!
PS - a less fun update (skip to maintain good vibes, stay to get pissed and/or call me a statist)
Interesting development: To all that previously have commented on this being a tax disaster: Well, it turns out that in my case, this is definitely correct. I'm constantly getting paid in fiat (cash, CashApp, or check, never direct deposit right now), converting to bitcoin, and then moving to my lightning node (except what I put in savings, which goes to multi-sig wallets). Now that I saw all the hubbub about the "single wallet" tax stuff in the last days before the new year, I realize that I'm basically that guy who is going to just have to make up cost basis guesses and hope that the men with guns realize I'm not trying to lie...
Anywho, kudos to all you non-tax payers out there or people that have the ability to get paid at the same wallet which they can pay bills from. Maybe I'll join you tax non-payers (just since it's so hard to pay them honestly and still have any time to work) when I have less dependents (at least fifteen years from now for any trigger happy IRS guys paying attention)...
originally posted at https://stacker.news/items/834254
-
 @ a38a5cd0:92b1b8f0
2024-12-30 13:31:02
@ a38a5cd0:92b1b8f0
2024-12-30 13:31:02I was born and raised in Europe—Switzerland, to be exact—and we’ve always had a special relationship with Europe or the EU. Although Switzerland is in the middle of Europe, it has always been isolated—not politically speaking, but through clever negotiations and an attractive financial marketplace.
But it’s still part of Europe, and whenever we drove to Germany, Austria (where I now live), or Italy, we always felt at home. Everyone was welcoming and accepted that Switzerland is the ‘special kid’ on the continent.
This is one of Europe’s superpowers. It lives off its different cultures. Other than America, I’m sorry to compare it, but it feels like many Americans have never left their own country; we can drive somewhere for three hours and pass two or even three countries.
Citizens speak different languages in each country, but we get along because there is a certain ‘European Vibe’ around. These different cultures and societies enable you to find communities where you feel at home and can be the best version of yourself—at least, that’s what I believe and have experienced.
However, the last 15 years have been challenging. Not only from a business standpoint, we tend to regulate and not innovate, but also from a political standpoint.
The EU and specific countries such as Sweden, Germany, and even Austria are fighting with high immigration, the Euro crisis – casually losing over 65% of its purchasing power this past decade – and ever-increasing debt.
Combine that with a keen interest by the majority of the population in Europe for Communism or Socialism. Please don’t ask me why it’s so popular in Europe. I think it could be an outcome of the world war situations where we never wanted to shift extremely right again. Or maybe the openness of the European spirit invites this thoughtfulness.
These ideologies don’t want the individual to succeed. For the better of all, it has always been at the center of these political movements. Inevitably, this idea leads to more poverty, more centralization, and, in the end, less democracy (the favorite word of any left-leaning politician in Europe) with a dictator at the whelm.
For some weird reason, we don’t want individual Europeans to succeed; instead, we have a collectivism that punishes brilliant ideas and nurtures the ever-increasing state.
So, why are you writing this essay then, Joël? Are you a right winger who’s just here to tell us Communism failed and we should do something else? NO! While my political views can definitely be described as conservative, I’m not associated with the right side of the aisle and would describe myself as a libertarian. However, for the European standard, I might be categorized as ‘right-wing,’ but who isn’t these days?!
But to answer the question, I think we have a secret weapon. Many of these freaks are either ignoring or deliberately downplaying because they’re scared of losing power and trying everything to forbid it.
You might have guessed by the title this secret weapon is Bitcoin!
There are apparent reasons why Bitcoin is the ultimate solution for Europe. These reasons are well known, from its scarcity to its natural state as the best reserve asset and its average value increase of 45% each year for the past decade. From a monetary perspective, these points make perfect sense.
However, there is more to the orange coin, especially from a polarization perspective. In Europe, the left and right are so far apart that it’s laughable. Bitcoin is the only asset or ecosystem enabling people from two corners to reunite and agree on something.
In Europe, in particular, this is something like human rights and privacy for every individual on the continent. It doesn’t matter whether you’re in Switzerland, Germany, or Portugal. Every citizen of these countries is rooting for human rights and the right to protect your most precious secrecies from third parties, aka the ever-increasing security state.
If you take a closer look at most political debates in Europe, both the left and the right agree that citizens should be able to protect their physical or digital properties and how to be more independent. Bitcoin enables you to do all of these things.
Additionally, mining can be an excellent catalyst for all parties to unite if you examine topics such as energy independence. Lefties can choose renewable energy, while right-wingers can embrace a free and healthy energy market. Bitcoin also enables this.
However, the most significant and crucial point is that Bitcoin will enable all nations to be independent again. Many countries lost their sovereignty mainly due to the EU and the Euro.
We no longer talk about each country’s interests; instead, we insert the sentence, ‘Anything that’s good for the EU.’ While the EEA (European Economic Area) was a noble idea that facilitated trade and economic output in Europe, it was abused and became a regulatory superpower with the EU.
You can see the consequences of this from the sheer number of companies who left Europe or international companies who treat Europe as a secondary market with little interest.
If Nations can regain sovereignty again and nurture their economic or sociological advantages, every citizen in these countries will have a new outlook on life.
All it takes for each of them to make the most important step in their Bitcoin journey; being curious enough to learn more about it, spending some time learning the fundamentals, and getting off zero!
One European nation with great potential for this is my home country, Switzerland. We’re the golden European standard for democracy, sovereignty, a strong economy, and a country where everyone can succeed.
After all, fellow Bitcoiners have already taken the initiative to add Bitcoin to the Swiss National Bank (SNB) ’s balance sheet and have already invested in MicroStrategy.
All it takes is the last step, which is to stack Sats as a strategic treasury reserve asset. As a fellow Swiss citizen and someone who works at a Swiss Bitcoin-only company, I would welcome this step and would love to help out!
To quote Walt Disney: ‘The way to get started is to quit talking and begin doing.’ So go ahead, Europe, and get started! Block space is limited, and 2140 is edging closer every ten minutes with a new block!
-
 @ 1cb14ab3:95d52462
2025-01-02 21:31:48
@ 1cb14ab3:95d52462
2025-01-02 21:31:48
No. 6 - Zhujiajiao Canal Chasing

For a tranquil escape from the hustle and bustle of the city cruise to Zhujiajiao -- an epic water town dating back to the Ming and Qing dynasties. It's only about 50 kilometers from the downtown and makes for an easy day trip. Hop on the subway and get there in an hour. Zhujiajiao has canals, bridges, and ancient buildings, offering a glimpse into the town's rich history. Take a boat ride along the canals for the best views of traditional houses and temples. Then explore the town on foot and get lost in attractions like the Kezhi Garden, Yuanjin Temple, and the Qing Dynasty Post Office. Don't forget to grub-up with all of the great food vendors nearby.
No. 7 - China Art Museum

China Art Museum is absolutely worth the trip solely for its awe-inspiring architecture. The towering structure casts a tall shadow over bystanders. Step inside and you'll find a world of art waiting. The blend of permanent and temporary exhibits offers hours of art-gazing. Give yourself at least half a day to fully immerse in the creative haven in Pudong. To get to the China Art Museum, you can take Line 2 of the Shanghai Metro and get off at the Pudong Avenue Station (Chinese: 浦东大道站). The museum is located near Exit 4 of the station.
No. 8 - Days on The West Bund

Hands down my favorite place in Shanghai. This spot is the go-to for a perfect weekend under the sun. You'll find me setting up a blanket with beer, cards, and snacks, along with a slackline and spike ball setup nearby, surrounded by dogs running around, enjoying the company of old and new friends. When you want a little movement enjoy some climbing, skating, running, or basketball after work. The West Bund is an oasis amidst the chaos of the city. But beware - its popularity is growing, so tread lightly.
No. 9 - Nights Under the Lupu Bridge
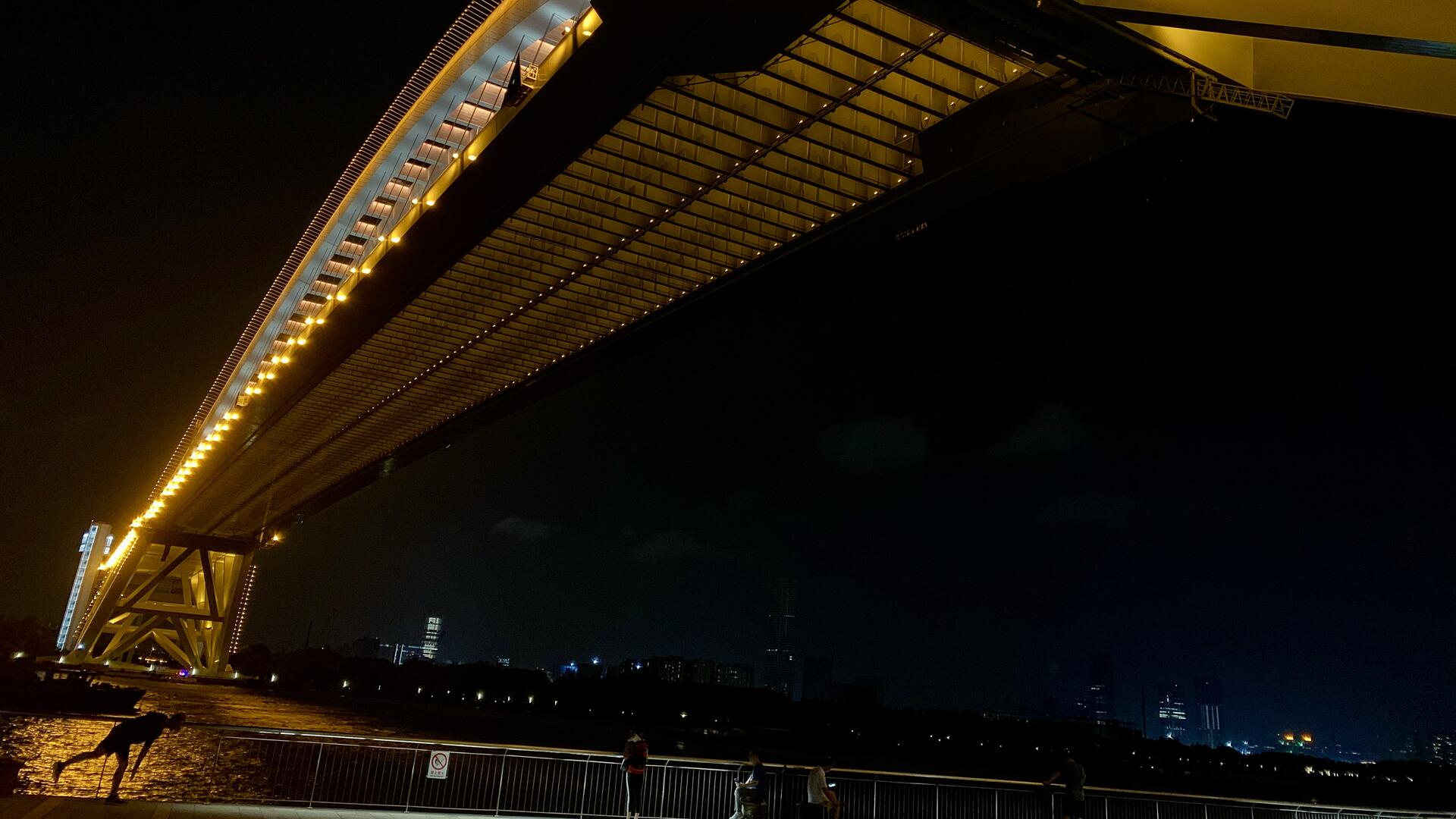
Nights under the Lupu Bridge are where it's at, man. Hop on your scooter and cruise over for the ultimate skyline views. Stroll along the walkway, munch on street food, sip drinks, and groove to live tunes. Street vendors serve up traditional snacks and crafts, and the vibe gets lit with spontaneous performances and games. Get ready to soak up the electric energy of Shanghai's Lupu Bridge at night."
No. 10 - A Weekend on Chongming

Escape the city hustle and find your peace on Chongming Island. A weekend getaway on this rural gem is just what you need. Chill out in a farmhouse, soak up the sunset, and enjoy the tranquility. Explore the natural wonders, visit the old museums, and feast on fresh seafood. End your days with a beach walk under the stars. Nothing beats a few nights away from the city chaos.
Additional Photos






Previous Guide in the Series:
An Expats Guide to the Best Spots in Shanghai: 001
Next Guide in the Series:
An Expats Guide to the Best Spots in Shanghai: 003
Find Me Elsewhere:
All images are property of Hes. Published 06.29.2024
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ 6734e11d:c7e34e8f
2024-12-29 18:07:00
@ 6734e11d:c7e34e8f
2024-12-29 18:07:00 -
 @ e31e84c4:77bbabc0
2024-12-02 10:44:07
@ e31e84c4:77bbabc0
2024-12-02 10:44:07Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
Fiduciary duty is the obligation to act in the client’s best interests at all times, prioritizing their needs above the advisor’s own, ensuring honesty, transparency, and avoiding conflicts of interest in all recommendations and actions.
This is something all advisors in the BFAN take very seriously; after all, we are legally required to do so. For the average advisor this is a fairly easy box to check. All you essentially have to do is have someone take a 5-minute risk assessment, fill out an investment policy statement, and then throw them in the proverbial 60/40 portfolio. You have thousands of investment options to choose from and you can reasonably explain how your client is theoretically insulated from any move in the \~markets\~. From the traditional financial advisor perspective, you could justify nearly anything by putting a client into this type of portfolio. All your bases were pretty much covered from return profile, regulatory, compliance, investment options, etc. It was just too easy. It became the household standard and now a meme.
As almost every real bitcoiner knows, the 60/40 portfolio is moving into psyop territory, and many financial advisors get clowned on for defending this relic on bitcoin twitter. I’m going to specifically poke fun at the ‘40’ part of this portfolio.
The ‘40’ represents fixed income, defined as…
An investment type that provides regular, set interest payments, such as bonds or treasury securities, and returns the principal at maturity. It’s generally considered a lower-risk asset class, used to generate stable income and preserve capital.
Historically, this part of the portfolio was meant to weather the volatility in the equity markets and represent the “safe” investments. Typically, some sort of bond.
First and foremost, the fixed income section is most commonly constructed with U.S. Debt. There are a couple main reasons for this. Most financial professionals believe the same fairy tale that U.S. Debt is “risk free” (lol). U.S. debt is also one of the largest and most liquid assets in the market which comes with a lot of benefits.
There are many brilliant bitcoiners in finance and economics that have sounded the alarm on the U.S. debt ticking time bomb. I highly recommend readers explore the work of Greg Foss, Lawrence Lepard, Lyn Alden, and Saifedean Ammous. My very high-level recap of their analysis:
-
A bond is a contract in which Party A (the borrower) agrees to repay Party B (the lender) their principal plus interest over time.
-
The U.S. government issues bonds (Treasury securities) to finance its operations after tax revenues have been exhausted.
-
These are traditionally viewed as “risk-free” due to the government’s historical reliability in repaying its debts and the strength of the U.S. economy
-
U.S. bonds are seen as safe because the government has control over the dollar (world reserve asset) and, until recently (20 some odd years), enjoyed broad confidence that it would always honor its debts.
-
This perception has contributed to high global demand for U.S. debt but, that is quickly deteriorating.
-
The current debt situation raises concerns about sustainability.
-
The U.S. has substantial obligations, and without sufficient productivity growth, increasing debt may lead to a cycle where borrowing to cover interest leads to more debt.
-
This could result in more reliance on money creation (printing), which can drive inflation and further debt burdens.
In the words of Lyn Alden “Nothing stops this train”
Those obligations are what makes up the 40% of most the fixed income in your portfolio. So essentially you are giving money to one of the worst capital allocators in the world (U.S. Gov’t) and getting paid back with printed money.
As someone who takes their fiduciary responsibility seriously and understands the debt situation we just reviewed, I think it’s borderline negligent to put someone into a classic 60% (equities) / 40% (fixed income) portfolio without serious scrutiny of the client’s financial situation and options available to them. I certainly have my qualms with equities at times, but overall, they are more palatable than the fixed income portion of the portfolio. I don’t like it either, but the money is broken and the unit of account for nearly every equity or fixed income instrument (USD) is fraudulent. It’s a paper mache fade that is quite literally propped up by the money printer.
To briefly be as most charitable as I can – It wasn’t always this way. The U.S. Dollar used to be sound money, we used to have government surplus instead of mathematically certain deficits, The U.S. Federal Government didn’t used to have a money printing addiction, and pre-bitcoin the 60/40 portfolio used to be a quality portfolio management strategy. Those times are gone.
Now the fun part. How does bitcoin fix this?
Bitcoin fixes this indirectly. Understanding investment criteria changes via risk tolerance, age, goals, etc. A client may still have a need for “fixed income” in the most literal definition – Low risk yield. Now you may be thinking that yield is a bad word in bitcoin land, you’re not wrong, so stay with me. Perpetual motion machine crypto yield is fake and largely where many crypto scams originate. However, that doesn’t mean yield in the classic finance sense does not exist in bitcoin, it very literally does. Fortunately for us bitcoiners there are many other smart, driven, and enterprising bitcoiners that understand this problem and are doing something to address it. These individuals are pioneering new possibilities in bitcoin and finance, specifically when it comes to fixed income.
Here are some new developments –
Private Credit Funds – The Build Asset Management Secured Income Fund I is a private credit fund created by Build Asset Management. This fund primarily invests in bitcoin-backed, collateralized business loans originated by Unchained, with a secured structure involving a multi-signature, over-collateralized setup for risk management. Unchained originates loans and sells them to Build, which pools them into the fund, enabling investors to share in the interest income.
Dynamics
- Loan Terms: Unchained issues loans at interest rates around 14%, secured with a 2/3 multi-signature vault backed by a 40% loan-to-value (LTV) ratio.
- Fund Mechanics: Build buys these loans from Unchained, thus providing liquidity to Unchained for further loan originations, while Build manages interest payments to investors in the fund.
Pros
- The fund offers a unique way to earn income via bitcoin-collateralized debt, with protection against rehypothecation and strong security measures, making it attractive for investors seeking exposure to fixed income with bitcoin.
Cons
- The fund is only available to accredited investors, which is a regulatory standard for private credit funds like this.
Corporate Bonds – MicroStrategy Inc. (MSTR), a business intelligence company, has leveraged its corporate structure to issue bonds specifically to acquire bitcoin as a reserve asset. This approach allows investors to indirectly gain exposure to bitcoin’s potential upside while receiving interest payments on their bond investments. Some other publicly traded companies have also adopted this strategy, but for the sake of this article we will focus on MSTR as they are the biggest and most vocal issuer.
Dynamics
-
Issuance: MicroStrategy has issued senior secured notes in multiple offerings, with terms allowing the company to use the proceeds to purchase bitcoin.
-
Interest Rates: The bonds typically carry high-yield interest rates, averaging around 6-8% APR, depending on the specific issuance and market conditions at the time of issuance.
-
Maturity: The bonds have varying maturities, with most structured for multi-year terms, offering investors medium-term exposure to bitcoin’s value trajectory through MicroStrategy’s holdings.
Pros
-
Indirect Bitcoin exposure with income provides a unique opportunity for investors seeking income from bitcoin-backed debt.
-
Bonds issued by MicroStrategy offer relatively high interest rates, appealing for fixed-income investors attracted to the higher risk/reward scenarios.
Cons
-
There are credit risks tied to MicroStrategy’s financial health and bitcoin’s performance. A significant drop in bitcoin prices could strain the company’s ability to service debt, increasing credit risk.
-
Availability: These bonds are primarily accessible to institutional investors and accredited investors, limiting availability for retail investors.
Interest Payable in Bitcoin – River has introduced an innovative product, bitcoin Interest on Cash, allowing clients to earn interest on their U.S. dollar deposits, with the interest paid in bitcoin.
Dynamics
-
Interest Payment: Clients earn an annual interest rate of 3.8% on their cash deposits. The accrued interest is converted to Bitcoin daily and paid out monthly, enabling clients to accumulate Bitcoin over time.
-
Security and Accessibility: Cash deposits are insured up to $250,000 through River’s banking partner, Lead Bank, a member of the FDIC. All Bitcoin holdings are maintained in full reserve custody, ensuring that client assets are not lent or leveraged.
Pros
-
There are no hidden fees or minimum balance requirements, and clients can withdraw their cash at any time.
-
The 3.8% interest rate provides a predictable income stream, akin to traditional fixed-income investments.
Cons
-
While the interest rate is fixed, the value of the Bitcoin received as interest can fluctuate, introducing potential variability in the investment’s overall return.
-
Interest rate payments are on the lower side
Admittedly, this is a very small list, however, these types of investments are growing more numerous and meaningful. The reality is the existing options aren’t numerous enough to service every client that has a need for fixed income exposure. I challenge advisors to explore innovative options for fixed income exposure outside of sovereign debt, as that is most certainly a road to nowhere. It is my wholehearted belief and call to action that we need more options to help clients across the risk and capital allocation spectrum access a sound money standard.
Additional Resources
-
River: The future of saving is here: Earn 3.8% on cash. Paid in Bitcoin.
-
MicroStrategy: MicroStrategy Announces Pricing of Offering of Convertible Senior Notes
Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
-
-
 @ fd208ee8:0fd927c1
2024-12-26 07:02:59
@ fd208ee8:0fd927c1
2024-12-26 07:02:59I just read this, and found it enlightening.
Jung... notes that intelligence can be seen as problem solving at an everyday level..., whereas creativity may represent problem solving for less common issues
Other studies have used metaphor creation as a creativity measure instead of divergent thinking and a spectrum of CHC components instead of just g and have found much higher relationships between creativity and intelligence than past studies
https://www.mdpi.com/2079-3200/3/3/59
I'm unusually intelligent (Who isn't?), but I'm much more creative, than intelligent, and I think that confuses people. The ability to apply intelligence, to solve completely novel problems, on the fly, is something IQ tests don't even claim to measure. They just claim a correlation.
Creativity requires taking wild, mental leaps out into nothingness; simply trusting that your brain will land you safely. And this is why I've been at the forefront of massive innovation, over and over, but never got rich off of it.
I'm a starving autist.
Zaps are the first time I've ever made money directly, for solving novel problems. Companies don't do this because there is a span of time between providing a solution and the solution being implemented, and the person building the implementation (or their boss) receives all the credit for the existence of the solution. At best, you can hope to get pawned off with a small bonus.
Nobody can remember who came up with the solution, originally, and that person might not even be there, anymore, and probably never filed a patent, and may have no idea that their idea has even been built. They just run across it, later, in a tech magazine or museum, and say, "Well, will you look at that! Someone actually went and built it! Isn't that nice!"
Universities at least had the idea of cementing novel solutions in academic papers, but that: 1) only works if you're an academic, and at a university, 2) is an incredibly slow process, not appropriate for a truly innovative field, 3) leads to manifestations of perverse incentives and biased research frameworks, coming from 'publish or perish' policies.
But I think long-form notes and zaps solve for this problem. #Alexandria, especially, is being built to cater to this long-suffering class of chronic underachievers. It leaves a written, public, time-stamped record of Clever Ideas We Have Had.
Because they are clever, the ideas. And we have had them.
-
 @ 1cb14ab3:95d52462
2025-01-02 21:24:19
@ 1cb14ab3:95d52462
2025-01-02 21:24:19
No. 11 - Evenings in Pujiang Town

A laid-back vibe in the heart of Shanghai. The area is packed with fantastic restaurants and offers serene views of canal reflections. It’s super easy to get there via the metro, making it a perfect evening escape. The charm lies in its simplicity; it’s the kind of place where you can take a leisurely stroll and truly unwind. If you’re lucky, you might catch a gorgeous sunset mirrored in the water.
No. 12 - Sunbathing at Jinshan Beach

Okay, Jinshan Beach isn’t winning any awards for “World’s Nicest Beach” (it’s man-made and, well, it’s China), but there’s something unbeatable about a sunny day by the water. Grab a towel, soak up some rays, and embrace the experience. There’s also a variety of beachside snacks and vendors that add to the laid-back vibe. While it’s not luxury, it’s a solid way to escape the hustle and bustle of the city.
No. 13 - Rooftop Chasin’

The best sights of the city are often in places you’re not supposed to be. Feeling adventurous? Try finding your way onto the roof of an apartment or office building. It might take a little finesse, but the reward is worth it: breathtaking views few others have ever seen. The city feels different from up high—quiet, sprawling, and almost surreal. Just make sure to stay safe and respectful; not every rooftop adventure is worth the risk.
No. 14 - Shanghai Disneyland

This might not count as a classic “expat spot,” but skipping a trip to the happiest place on earth while in Shanghai would be a mistake. The Tron and Pirates of the Caribbean rides are next-level—just prepare to wait. The long lines and bustling crowds are part of the adventure, so make the most of it! Pro tip: get there early to maximize your day and snag a good spot for the evening fireworks. It’s a little slice of magic you won’t forget.
No. 15 - Insanity on the Maglev
In five years of living in China, I somehow only rode the Maglev once. If you haven’t yet, don’t miss out! There’s something surreal about flying at 368 km/h as the world blurs past your window. It’s a feat of engineering that makes you appreciate just how far technology has come. Even if you don’t need to catch a flight, the ride itself is worth the experience.
Additional Photos












Previous Guides in the Series:
An Expats Guide to the Best Spots in Shanghai: 001
An Expats Guide to the Best Spots in Shanghai: 002
Find Me Elsewhere:
All images taken by Hes. Published 01/02/2025
-
 @ 714f9dc3:76659adb
2025-01-02 20:47:45
@ 714f9dc3:76659adb
2025-01-02 20:47:45Last week, I was reading “The Air We Breathe”, by Glen Scrivener. It’s about “How We All Came to Believe in Freedom, Kindness, Progress, and Equality”, and it explores the Christian roots of the values we prize in today's western society. It’s all around us, but we don’t really know where it came from: It’s the air we’re breathing. The ideas and ethics behind Christianity, whether you believe in them or not, are embedded in our culture.
As I was reading this, I saw so many parallels with Bitcoin, so wanted to list them below and share some of my thoughts. Can Bitcoin also become “The Air We Breathe”? Or in plebs words: hyperbitcoinization? Can Bitcoin become so ubiquitous that it becomes normal? Can there be a world in which we don’t even know where Bitcoin came from? It would be a world with many similar views as with today's view on Christianity. It becomes the air we breathe, something that used to be a counterculture that over time became ubiquitous. What can we learn from it?
These are my ten parallels of Bitcoin with the early days of Christianity. 1. Separation from state 2. From obscure counterculture to dominant force 3. Exponential grassroots growth 4. Conversion of emperors/politicians 5. Sudden tolerance and protection for ideology 6. Fall of the empire, end of the status quo 7. Missionaries spreading the word 8. Persuasion and education are key 9. Age of Enlightenment
Note: I’m no expert on Christianity, nor a historian of the Roman Empire, and I know just a bit about Bitcoin. See this as a thought experiment.
1. Separation from state In all fairness, I’m not the first to draw this first parallel. It was Satoshi Nakamoto themself who made the connection even before Bitcoin was available to the public, with several hints pointing back to important dates and moments in Christian history. The big parallel here is the “separation of money and state” and “separation of church and state”.
Before going back to the early days of Christianity in the first centuries AD, I first want to draw this parallel with Satoshi.
It’s 1517. The German Priest Maarten Luther writes his Ninety-five Theses, and nails this on the church doors in Wittenberg. The theses are also known as the “Disputation on the Power and Efficacy of Indulgences”. He kickstarted a movement with a radical new idea for that time: The separation of the church from the state.
The Catholic Church had become one with the state. Via the means of indulgences, there was an ability to pay for your redemption. The church was corrupted by money, power and politics. The church and indulgences replaced the need for personal responsibility and an individual faith with money and perverse structures.
Reformation Day is a Protestant Christian religious holiday celebrated on 31 October in remembrance of the onset of the Reformation. But the 31st of October is also the day in which Satoshi shared his pamphlet with the world: in 2008 they published the Bitcoin Whitepaper. It kickstarted a movement with a radical new idea for that time: The separation of the money from the state.
But this was not Satoshi’s only hint. Another one is the date of Bitcoin’s Genesis Block: January 3, 2009. It was the day that the idea of the separation of money and the state became reality, more than just an idea in an individual's mind.
Did you know that Maarten Luther was excommunicated from the Catholic Church in 1521 by Pope Leo X for sparking this revolutionary new way of thinking (and being). It happened on January 3 as well. I bet Satoshi Nakamoto knew.
To be fair, this parallel is not new and known by many bitcoiners. But it’s a good introduction to the topic, and after reading “The Air We Breathe: How We All Came to Believe in Freedom, Kindness, Progress, and Equality”, I automatically started to see more parallels between (the early days of) Christianity and todays adoption of Bitcoin. Because it was of course not Maarten Luther who sparked these rebellious thoughts in 1500, but it was Jesus himself approx. 2000 years ago.
Let’s go back from the 1500s to the first decades AD to the beginning of this radical new belief system. During the dominance of the Roman empire in the Mediterranean and much of Europe, Western Asia and North Africa, someone told a story that opposed every mainstream paradigm.
Jesus’ idea was radically different from the belief systems of that day. He preached Freedom, Kindness, Progress, and Equality in a world that was full of Debauchery and Violence, with Gladiator Games, Slavery, Public Crucifixion, and Brutalities. The belief system of that time was not like todays. There were superior races (Greek/Romans over barbarians), superior sexes (man over women), superior classes (free man over slaves) and the concept of justice was more something in the realm of “restoring rights of those that were superior”, than “equality for all, men and women, Greek and barbarian, free and slave”.
Jesus opposed the status quo. It started small and irrelevant; as a counterculture. But it didn’t stay that way.
2. From obscure counterculture to dominant force In “The Air We Breathe”, Scrivener asks the question: “How did the obscure, marginal Jesus movement of the 1st century become the dominant religious force in the Western world in a few centuries?”
Important to know, is that the Christian faith was the opposite of the narrative. Concepts like Freedom, Kindness, Progress, and Equality didn’t exist in the Roman Empire. Human rights neither. Individual rights neither. The emperor was almost de facto God himself.
Early Christians were persecuted for preaching a different story: that God is NOT the ruler of the empire. Jesus preached the separation of politics from God; separating faith from the state. As a result, he was crucified, and many of his followers were killed by Nero (between 54 and 68 AD), Domitian (81–96 AD), Trajan (98–117 AD) and Decius (249–251 AD). This new narrative was a thread for the Roman rulers.
Draw the parallels of how there have been many attempts to “kill” bitcoin, not with physical persecution but with an information war. Not by physical violence, but by misinformation. Bitcoin threatens the status quo, just like Christianity threatened the Roman Empire.
You see?
But how is the obscure movement of Bitcoin in the 20th century becoming the dominant force, similar to the question that Scrivener asked about Christianity? Perhaps the answer lies in the following parallel.
3. Exponential grassroots growth Sociologist Rodney Stark estimates in “The Rise of Christianity” that from the time of the first Easter, the church began growing at a rate of 40% per decade, a modest but relentless 3.4% per year. By the year 300, Christians numbered perhaps 6 million: about a tenth of the empire.
Despite pushbacks, the army of believers continued to grow. Grassroots, peer-to-peer. It was not the state-religion, it was a peaceful army of believers that spread the word, resulting in an exponential growth of its followers. The counterculture became more and more dominant.
You may see what I’m doing here. It was basically the meme that all Bitcoiners know: Gradually, then suddenly. Against the current.
4. Conversion of emperors/politicians In 312 a big change happened: Emperor Constantine converted to Christianity. As Stark writes, "Constantine's conversion would better be seen as a response to the massive exponential wave in progress, not as its cause".
Are we living in that same era, where nation states start to embrace Bitcoin? Where politicians don’t oppose as strongly anymore, but are flirting with the idea of embracing it? And again the parallel: it’s responsive to the exponential wave of progress, not as its cause.
Whether Constantine is Nayib Bukele, Donald Trump, or Milei: it doesn’t matter. It’s the dynamic that matters. The counterculture becomes so dominant, that the “rulers” of the world are wanting to be part of it. Which will be followed by “rules” that favour the ideology, movement, and beliefs.
5. Tolerance and protection for ideology In 313 Constatines Edict of Milan granted freedom to Christians that were remarkable for that time and a model for religious toleration for the coming centuries.
The tide was turning, and by 380 Emperor Theodosius made Christianity Rome's official religion, more than half the population had already converted. In a few short centuries Christianity had gone from radical counterculture to dominant cultural power. This was an extraordinary shift in the church's relationship with the world. The edict expressly grants religious liberty to Christians, who had been the object of special persecution, but also goes even further and grants liberty to all other religions. And then, in 410, the world itself changed.
It changed from grassroots, bottom-up adoption to some kind of nation state adoption. One that was driven by decrees and edicts, instead of the analog cyberhornets of that day. Actually, the ideas of Indulgences were introduced via these Edicts, something that Maarten Luther actually was fighting against in the 1500s.
The world changed from the state-less Christian belief and moved (back) towards a system in which the state and church were connected again. Yes — the Roman Catholic Church. Until the previously mentioned critics during the Reformation.
6. Fall of the empire, end of the status quo When people speak of the fall of the Roman Empire, they usually mean in the 5th century when the western half fell. But there was also an eastern half, known as the Byzantine Empire (with its capital in what is modern-day Istanbul).
How did this relate to the movement that once was Cult, and now suddenly had become Culture?
It was Augustine, the north African bishop (354-430), who laid the foundation for a new philosophical, theological, and legal system. He distinguished between the fragile earthly realm and the eternal heavenly kingdom. Rome was “a city of man”, which fell. But the “city of God” was forever. He continued to separate the Roman Catholic Church from the faith that it once was. This distinction was vital, and it gave rise to the concept of "the secular realm". He planted the first ideas of "the separation of church and state" again, which started to spread throughout Europe during the supposedly "sandy desert" of the Middle Ages.
The parallel and lesson here might be that narratives can be taken over, for the worse. And that it takes centuries to take back the narrative, but/and only after an empire has fallen. Whether we refer to “The Fourth Turning” by William Strauss and Neil Howe or “Changing World Orders” by Ray Dalio. There is something to preserve, and it needs active monitoring and pushbacks!
7. Missionary, spreading the word The way the church sought to spread its influence would become a question that would take many centuries (and many failures) to settle. In the past, empires sought to spread their influence almost always by force. Christianity has been a missionary faith from the beginning. It was for this reason that Pope Gregory the Great sent Augustine to Britain to convert the Anglo-Saxons.
Augustine was commanded by Gregory to use only "gentle means". His goal was persuasion. His method was teaching and preaching. And he was successful, converting King Aethelbert of Kent and becoming the first Archbishop of Canterbury.
You see what I’m talking about again: the parallel is simple. Bitcoin is a similar peaceful revolution, a missionary movement, of those that wish to see their Cult turn into a Culture. “Genle means”, teachings, persuasions. Or in pleb terminology: Orangepilling.
8. Persuasion and education are key Over the next decades and centuries, this movement continued. English Benedictine monk (675-754) Boniface was sent from the previously “barbarian” Britain to “orangepill the East” – in this case the Saxons in the Germanic lands. In the words of his advisor, the Bishop of Winchester, his goal was "to convince them by many documents and arguments". This mission of persuasion and education was largely successful. Today he’s better known as “the Apostle to the Germans". He was killed in The Netherlands (Dokkum).
Boniface kept to a policy of non-violence and non-retaliation, even to the point of death. Another famous writer about this topic, Tom Holland, summarises the lesson we learn from Boniface: "to convert was to educate".
In the following century this lesson was sorely needed by the Frankish king Charles the Great, aka Charlemagne (742-814). Charlemagne's path to power was a brutal one. When the Saxons stood in his way, Charlemagne beheaded 4,500 of them in a single day. There are concrete reasons why "getting medieval" might be associated today with brutality.
Is “Bitcoin as Legal Tender”, whether this is peaceful or violently, the way to go? Are we “getting medieval” with these kind of measures, in order to go from Cult to Culture, from counterculture to dominant culture, in which we lose the true essence of our revolution of separation of the state from the matter?
9. Age of Enlightenment Alcuin of York (735-804), was bold enough to write to Charlemagne directly with his criticism. "A person can be drawn into the faith, not forced into it". Be a lighthouse, not a tugboat!
The church's official teaching would later agree with Alcuin's position. In the 12th century all "harsh means" were forbidden since faith arises from the will, not compulsion. Enlightenment comes through education and persuasion.
There’s work to do. Grassroots. Education. Peer-to-peer. Not directed by politicians, nor opposed by those in power. Through education and persuasion. Rules without rulers. Because eventually, with the Crusades and the Spanish Inquisition, there are stark examples of the church using “harsh means" again. Forcing Bitcoin on people will never be the way: it’s a cheat code to the end goal. In order to succeed, we’ll need to be a missionary.
Final words I don’t want in any way to compare Christianity in itself as a faith, and Bitcoin as a technology, with each other. I enjoyed exploring the sociological phenomena between two countercultures, the grassroots movement and missionary parallels between both of them. Satoshi gave the first assist, with the 31st of October (Whitepaper Day) and the Genesis Block on January 3rd.
Let’s not mix religion with monetary systems, even though there are many similarities between certain movements. That’s not my goal for sharing this brain dump. But let’s learn from the past, from Constatine’s Edict and from Augustine, from Charlemagne (and especially Alcuin of York), from Boniface and from Maarten Luther. And from Satoshi Nakamoto.
-
 @ 4ba8e86d:89d32de4
2024-11-14 09:17:14
@ 4ba8e86d:89d32de4
2024-11-14 09:17:14Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ bd32f268:22b33966
2025-01-02 19:30:46
@ bd32f268:22b33966
2025-01-02 19:30:46Texto publicado por Foundation Father @FoundationDads e traduzido para português.
Assumir responsabilidades numa época efeminada como a nossa é um superpoder.
Algumas pessoas não sabem o que significa "assumir responsabilidades", no entanto, porque nunca tiveram um pai ou outra pessoa que as ama-se o suficiente para lhes ensinar.
Então, aqui está como assumir responsabilidades.
Lembra-te que não és uma pessoa desamparada e incompetente.
As coisas não te acontecem simplesmente enquanto olhas fixamente com a boca aberta, usando todo o teu poder cerebral para te lembrares de como respirar.
Tu tens poder de ação.
Mantém estas perguntas em mente:
"Que papel desempenhei eu nesta situação ou como ajudei a formar o sistema em que estou inserido?"
"O que posso fazer agora mesmo para começar a corrigi-lo, por mais pequeno que seja?"
Aqui estão alguns exemplos de como aplicar estas perguntas.
 José Malhoa - Remédio
José Malhoa - RemédioSaúde
Estás com excesso de peso e cansado o tempo todo? Deprimido?
Começa a caminhar 30 minutos por dia. De preferência ao ar livre.
Pára de comer snacks.
Marca uma consulta com um médico para fazer análises ao sangue.
Todas estas coisas estão ao teu alcance.
Finanças
Estás a afogar-te em dívidas de cartão de crédito? Assumir responsabilidades significa reduzir drasticamente o teu consumo e iniciar um programa radical de pagamento do máximo de dívida que conseguires.
Obtém uma aplicação de orçamento e começa a planear.
Sentes-te preso no teu emprego sem futuro? Sentes que não ganhas o suficiente? Vai a entrevistas para vagas de emprego e descobre o teu verdadeiro valor no mercado.
Reserva 1 hora todas as noites para melhorares. A menos que já estejas a trabalhar em dois empregos, toda a gente tem pelo menos 1 hora todas as noites.
Arredores imediatos
Se vês algo que precisa de ser feito, simplesmente faz. Não te queixes disso. Não resmungues baixinho. Não desejes que alguém tratasse disso. Simplesmente faz e não peças permissão.
Guarda o carrinho de compras. Lava a caneca de café no lava-loiça. Arranca as ervas daninhas. Repara a parede. Se o quintal do teu vizinho estiver cheio de ervas, vai lá e corta a relva tu mesmo. Limpa a água do lava-loiça. Arruma a bancada. Leva o lixo para fora. Leva bom café para o escritório.
Os teus filhos
Muitos pais queixam-se do comportamento dos seus filhos como se não tivessem qualquer influência sobre o assunto. Mas os teus filhos farão o que tu os ensinaste a fazer.
"Fizemos o melhor que pudemos."
Não, não fizeram, e assumir responsabilidades significa admitir que foste permissivo e preguiçoso ou que querias sentir-te justo por não bater.
Que pequena coisa podes fazer agora mesmo para começar? Escolhe um único comportamento que queres que eles parem, senta-os e explica as consequências do comportamento. Pede desculpa por teres deixado andar durante tanto tempo.
Quando eles apresentarem o comportamento, aplica as consequências. Aconteça o que acontecer.
Os teus relacionamentos
Não tens amigos ou o teu grupo de amigos atual é uma má influência? Podes fazer novos amigos. Assumir responsabilidades significa admitir que a tua solidão é em grande parte auto-infligida.
O que podes fazer?
Começa a jogar ténis ou futebol. Existem ligas em todo o lado. Encontra uma boa igreja local e encontra maneiras de te envolver. Existem encontros para todo o tipo de atividade. Participa num que se alinhe com as tuas preferências. Quando estiveres em público, sorri mais e puxa conversa.
Depois de conheceres algumas pessoas, estabelece uma cadência regular. Agenda almoços semanais ou mensais e alterna entre algumas pessoas. Ou talvez café de manhã.
Não acontecerá da noite para o dia, mas dando pequenos passos consistentemente durante alguns meses e vais perceber que tens uma vida social.
Os teus erros
Se erraste, não te retires e escondas nem arranjes desculpas. Pede desculpa à pessoa que prejudicaste, diz-lhe porquê e oferece-te para compensar. Aceita as consequências com humildade.
Vais descobrir que nada te conquista mais respeito do que assumir os teus erros. Esta é a principal. Se aprenderes a fazer isto bem, cobrirá uma infinidade de pecados porque cria hábito. Mesmo que tenhas apenas 1% de culpa na situação, assumir a responsabilidade e pedir desculpa pelo teu 1% está a construir um certo grupo de músculos.
"Mas ele devia ter..." Pára com isso. Confiaste demasiado? Presumiste demasiado sem comunicar? Assume a responsabilidade por isso.
Estes exemplos podiam continuar para sempre, então vou parar e terminar com este princípio:
A tua resposta importa mais do que as tuas circunstâncias.
Existem vítimas reais, algumas de tragédias horríveis. Mas mesmo que não te tenhas atirado para areias movediças, ainda podes assumir a responsabilidade por como reages e pelo que escolhes fazer a seguir.
Às vezes, é agarrar numa corda de um transeunte e dizer: "Obrigado."
Não te afogues nas areias movediças até que alguém te dê uma palmadinha nas costas por quão difícil é para ti, e não continues a apontar para o teu tempo nas areias movediças para desculpares os teus fracassos.
Podes não ter escolhido uma batalha específica. Ainda podes assumir a responsabilidade por quão bem lutas a batalha. Num certo sentido, ninguém escolhe a principal batalha que enfrenta. Ninguém escolheu nascer. Ninguém escolheu a sua família. Ninguém escolheu as suas circunstâncias.
O mundo nunca será perfeito. Tens de assumir a responsabilidade pela tua parte dele de qualquer maneira. Pode ser difícil. Pode ser doloroso. Não te foi prometida uma vida fácil e sem dor.
Depois de começares a assumir responsabilidades, qual é o próximo passo?
Altura de assumir mais responsabilidades.
Por exemplo, se não tens problemas em fazer amigos e tens essa parte da tua vida resolvida, assume a responsabilidade por outra pessoa. Encontra um dos rapazes solitários na tua igreja que precisa de um amigo e adiciona-o à tua rotação de almoços.
A recompensa por assumir responsabilidades é subir de nível e, como consequência, as coisas devem tornar-se mais desafiantes.
Mas agora estás mais bem preparado para isso. Repete até morrer e, esperançosamente, a tua causa de morte será por viver e não por te queixares de não viver.
-
 @ 4ba8e86d:89d32de4
2024-11-07 13:56:21
@ 4ba8e86d:89d32de4
2024-11-07 13:56:21Tutorial feito por Grom mestre⚡poste original abaixo:
http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/240277/tutorial-criando-e-acessando-sua-conta-de-email-pela-i2p?show=240277#q240277
Bom dia/tarde/noite a todos os camaradas. Seguindo a nossa série de tutoriais referentes a tecnologias essenciais para a segurança e o anonimato dos usuários, sendo as primeiras a openPGP e a I2P, lhes apresento mais uma opção para expandir os seus conhecimentos da DW. Muitos devem conhecer os serviços de mail na onion como DNMX e mail2tor, mas e que tal um serviço de email pela I2P. Nesse tutorial eu vou mostrar a vocês como criar a sua primeira conta no hq.postman.i2p e a acessar essa conta.
É importante que vocês tenham lido a minha primeira série de tutoriais a respeito de como instalar, configurar e navegar pela I2P nostr:nevent1qqsyjcz2w0e6d6dcdeprhuuarw4aqkw730y542dzlwxwssneq3mwpaspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsyp5vcq Esse tutorial é um pré-requisito para o seguinte e portanto recomendo que leia-os antes de prosseguir com o seguinte tutorial. O tutorial de Kleopatra nostr:nevent1qqs8h7vsn5j6qh35949sa60dms4fneussmv9jd76n24lsmtz24k0xlqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgecq8f7 é complementar dado que é extremamente recomendado assinar e criptografar as mensagens que seguem por emails pela DW. Sem mais delongas, vamos ao tutorial de fato.
1. Criando uma conta de email no hq.postman
Relembrando: Esse tutorial considera que você já tenha acesso à I2P. Entre no seu navegador e acesse o endereço hq.postman.i2p. O roteador provavelmente já contém esse endereço no seu addressbook e não haverá a necessidade de inserir o endereço b32 completo. Após entrar no site vá para a página '1 - Creating a mailbox' https://image.nostr.build/d850379fe315d2abab71430949b06d3fa49366d91df4c9b00a4a8367d53fcca3.jpg
Nessa página, insira as credenciais de sua preferências nos campos do formulário abaixo. Lembre-se que o seu endereço de email aceita apenas letras e números. Clique em 'Proceed' depois que preencher todos os campos. https://image.nostr.build/670dfda7264db393e48391f217e60a2eb87d85c2729360c8ef6fe0cf52508ab4.jpg
Uma página vai aparecer pedindo para confirmar as credenciais da sua nova conta. Se tudo estiver certo apenas clique em 'Confirm and Create Mailbox'. Se tudo ocorrer como conforme haverá uma confirmação de que a sua nova conta foi criada com sucesso. Após isso aguarde por volta de 5 minutos antes de tentar acessá-la, para que haja tempo suficiente para o servidor atualizar o banco de dados. https://image.nostr.build/ec58fb826bffa60791fedfd9c89a25d592ac3d11645b270c936c60a7c59c067f.jpg https://image.nostr.build/a2b7710d1e3cbb36431acb9055fd62937986b4da4b1a1bbb06d3f3cb1f544fd3.jpg
Pronto! Sua nova conta de email na I2P foi criada. Agora vamos para a próxima etapa: como acessar a sua conta via um cliente de email.
2. Configurando os túneis cliente de SMTP e POP3
O hq.postman não possui um cliente web que nos permite acessar a nossa conta pelo navegador. Para isso precisamos usar um cliente como Thunderbird e configurar os túneis cliente no I2Pd que serão necessários para o Thunderbird se comunicar com o servidor pela I2P.
Caso não tenha instalado o Thunderbird ainda, faça-o agora antes de prosseguir.
Vamos configurar os túneis cliente do servidor de email no nosso roteador. Para isso abra um terminal ou o seu gestor de arquivos e vá para a pasta de configuração de túneis do I2P. Em Linux esse diretório se localiza em /etc/i2pd/tunnels.d. Em Windows, essa pasta se localiza em C:\users\user\APPDATA\i2pd. Na pasta tunnels.d crie dois arquivos: smtp.postman.conf e pop-postman.conf. Lembre-se que em Linux você precisa de permissões de root para escrever na pasta de configuração. Use o comando sudoedit
para isso. Edite-os conforme as imagens a seguir:
Arquivo pop-postman.conf https://image.nostr.build/7e03505c8bc3b632ca5db1f8eaefc6cecb4743cd2096d211dd90bbdc16fe2593.jpg
Arquivo smtp-postman.conf https://image.nostr.build/2d06c021841dedd6000c9fc2a641ed519b3be3c6125000b188842cd0a5af3d16.jpg
Salve os arquivos e reinicie o serviço do I2Pd. Em Linux isso é feito pelo comando:
sudo systemctl restart i2pdEntre no Webconsole do I2Pd pelo navegador (localhost:7070) e na seção I2P Tunnels, verifique se os túneis pop-postman e smtp-postman foram criados, caso contrário verifique se há algum erro nos arquivos e reinicie o serviço.Com os túneis cliente criados, vamos agora configurar o Thunderbird
3. Configurando o Thunderbird para acessar a nossa conta
Abra o Thunderbird e clique em criar uma nova conta de email. Se você não tiver nenhum conta previamente presente nele você vai ser diretamente recebido pela janela de criação de conta a seguir. https://image.nostr.build/e9509d7bd30623716ef9adcad76c1d465f5bc3d5840e0c35fe4faa85740f41b4.jpg https://image.nostr.build/688b59b8352a17389902ec1e99d7484e310d7d287491b34f562b8cdd9dbe8a99.jpg
Coloque as suas credenciais, mas não clique ainda em Continuar. Clique antes em Configure Manually, já que precisamos configurar manualmente os servidores de SMTP e POP3 para, respectivamente, enviar e receber mensagens.
Preencha os campos como na imagem a seguir. Detalhe: Não coloque o seu endereço completo com o @mail.i2p, apenas o nome da sua conta. https://image.nostr.build/4610b0315c0a3b741965d3d7c1e4aff6425a167297e323ba8490f4325f40cdcc.jpg
Clique em Re-test para verificar a integridade da conexão. Se tudo estiver certo uma mensagem irá aparecer avisando que as configurações do servidores estão corretas. Clique em Done assim que estiver pronto para prosseguir. https://image.nostr.build/8a47bb292f94b0d9d474d4d4a134f8d73afb84ecf1d4c0a7eb6366d46bf3973a.jpg
A seguinte mensagem vai aparecer alertando que não estamos usando criptografia no envio das credenciais. Não há problema nenhum aqui, pois a I2P está garantindo toda a proteção e anonimato dos nossos dados, o que dispensa a necessidade de uso de TLS ou qualquer tecnologia similar nas camadas acima. Marque a opção 'I Understand the risks' e clique em 'Continue' https://image.nostr.build/9c1bf585248773297d2cb1d9705c1be3bd815e2be85d4342227f1db2f13a9cc6.jpg
E por fim, se tudo ocorreu como devido sua conta será criada com sucesso e você agora será capaz de enviar e receber emails pela I2P usando essa conta. https://image.nostr.build/8ba7f2c160453c9bfa172fa9a30b642a7ee9ae3eeb9b78b4dc24ce25aa2c7ecc.jpg
4. Observações e considerações finais
Como informado pelo próprio site do hq.postman, o domínio @mail.i2p serve apenas para emails enviados dentro da I2P. Emails enviados pela surface devem usar o domínio @i2pmai.org. É imprescindível que você saiba usar o PGP para assinar e criptografar as suas mensagens, dado que provavelmente as mensagens não são armazenadas de forma criptografada enquanto elas estão armazenadas no servidor. Como o protocolo POP3 delete as mensagens no imediato momento em que você as recebe, não há necessidade de fazer qualquer limpeza na sua conta de forma manual.
Por fim, espero que esse tutorial tenha sido útil para vocês. Que seu conhecimento tenha expandido ainda mais com as informações trazidas aqui. Até a próxima.
-
 @ e1d968f7:5d90f764
2025-01-02 18:38:14
@ e1d968f7:5d90f764
2025-01-02 18:38:14When I first started as an escort, I didn’t fully appreciate just how important fantasy would be in this line of work. At first, I thought it was all about simple physical attraction or the kind of sexual desires you might see portrayed in films or novels. But the deeper I’ve gotten into this profession, the more I’ve realised that fantasy is so much more than that. It's woven into the very fabric of what I do, and it’s not just about sex—it's about identity, power, and, more often than not, a sense of escape.
For many of my clients, it’s not just about being with someone physically; it’s about creating a space where they can step out of their everyday lives and explore parts of themselves they don’t often get to. I’ve come to see fantasy as an incredibly powerful tool—not just for my clients, but for myself, too.
The Many Faces of Fantasy
Every time, I meet clients with different fantasies. Some want to explore particular sexual scenarios or role-play, while others are after something much more subtle—an emotional connection or a specific kind of attention they aren’t getting elsewhere. It’s not just about the physical; it’s about the mental, the emotional, and sometimes even the psychological needs that get wrapped up in these fantasies.
What’s always struck me is how diverse those desires can be. Sometimes, a client just wants to be listened to, to feel like they’re the centre of attention for a few hours without any distractions. For others, it’s about stepping into a role they never could in their daily life—maybe they want to feel powerful or dominant, or perhaps they crave vulnerability and want to surrender control. I’ve played all kinds of roles—whether it’s a confident professional, a shy lover, or even a nurturing figure—and each fantasy brings its own set of dynamics.
But the most interesting part of it all? It’s the way these fantasies often go beyond what I ever imagined them to be. They’re not always as simple as "acting out a scenario." Sometimes, it’s just about creating the right atmosphere—being present, attentive, and creating a safe space where someone can let their guard down. It’s an art, really.
My Own Fantasies and Boundaries
A question I get asked often is whether I have my own fantasies and how they fit into this work. To be honest, it’s something I don’t talk about too much, but I think it’s an important part of this journey. While I’m here to make my clients’ fantasies come to life, I also have my own boundaries, desires, and needs. There’s a delicate balance between providing what someone else wants and ensuring I don’t lose sight of myself in the process.
I’ve learned that I have to stay grounded in my own identity. I can get swept up in someone else’s world, their desires, and fantasies, but it’s crucial that I don’t lose my sense of self along the way. It’s all too easy to slip into the role of someone else, but I’m still Rebecca—the woman with my own life, my own boundaries, and yes, my own fantasies.
The Mutual Exchange
I’ve come to realise that fantasy is a two-way exchange. While I’m helping a client explore their deepest desires, I, too, am learning something new about myself—about my capacity for connection, my ability to empathise, and my own sense of empowerment. It’s not always just about fulfilling someone else’s needs; it’s also about the journey I take with them, even if just for a brief time.
I’ve often thought of myself as a kind of mirror. In many ways, I reflect what my clients are feeling, but at the same time, I’m learning more about myself through these interactions. It’s strange, isn’t it? How a job that might seem so transactional on the surface can actually be a profound exchange of emotions and experiences. The line between reality and fantasy blurs at times, and it’s easy to forget that this is work.
Fantasy as Empathy
What I’ve realised, though, is that fantasy is more than just a form of escapism—it’s an art of empathy. The best parts of escorting aren’t just about giving someone what they want; they’re about creating an experience where both of us can feel seen, heard, and understood. That’s what makes the work so fulfilling for me. It’s not always about fulfilling the exact fantasy someone has in mind, but about understanding them deeply and connecting in a way that feels real, even if it’s only for an hour or two.
I’ve learned that empathy is key. It's not just about acting out a role, but about tapping into what someone truly needs—sometimes in ways they’re not even fully aware of. And when I can do that, the experience becomes something far more meaningful than just a physical transaction. It’s a shared moment of vulnerability, trust, and connection.
Final Thoughts
Looking back on my journey, I see that fantasy isn’t just a part of the job—it’s a central part of my growth as an escort. It’s not just about fulfilling desires; it’s about learning to navigate the complexities of human emotion, to offer a safe space for exploration, and to understand how deeply interconnected our desires and identities really are.
And while I’ll continue to help clients explore their fantasies, I’m also exploring my own. The job isn’t just about meeting others’ needs; it’s also about learning more about myself, my boundaries, and my capacity for empathy. It’s a constant journey, but one that makes me feel connected to the deeper aspects of humanity—something I never expected when I first started.
Until tomorrow,
Rebecca x -
 @ ccc8ee23:9f3d9783
2024-12-23 22:03:15
@ ccc8ee23:9f3d9783
2024-12-23 22:03:15Chef's notes
Indulge in tender, golden-fried chicken breast, crunchy with every bite. Nestled on a bed of steamed rice, this dish is elevated by a rich, velvety curry sauce, infused with the warmth of fragrant spices and the umami depth of soy.
Paired with vibrant vegetables for a harmonious balance of textures and flavors, this comforting classic promises to delight your soul.
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 30 min
- 🍽️ Servings: 2
Ingredients
- Chicken Fillet 250 grams
- Potato 100 grams
- Egg 1 pc
- Curry block 2 pcs or 20 grams
- breadcrumbs 100 grams / 2 cups
- flour 20 grams
- Cooking oil (for frying)
- chicken or vegetable stock 500ml
- soy sauce 1 tbsp
- Seasoning
- onion 1 pc, finely chopped
- garlic cloves 2 pcs, minced
- carrot 1 pc, chopped
Directions
- Chicken Katsu: Pound the chicken breasts until about 1/2 inch thick. Season with salt and pepper. Coat each piece in flour, then dip in beaten egg, and finally coat with breadcrumbs. Heat oil in a pan and fry the chicken for about 3-4 minutes on each side, until golden brown and fully cooked. Place on paper towels to drain.
- Make Curry Sauce: In a pan, sauté the onion, garlic, add potato and carrot until soft. Gradually add curry block and the stock, stir well. Simmer for 5-10 minutes until thickened. Add seasoning and soy sauce to taste.
- Plating: Slice the cooked chicken katsu and place it over a bed of steamed rice. Pour the curry sauce on the side or over the chicken. Garnish with chopped green chilies.
-
 @ 3bf0c63f:aefa459d
2024-03-19 14:01:01
@ 3bf0c63f:aefa459d
2024-03-19 14:01:01Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ 76c71aae:3e29cafa
2024-08-13 04:30:00
@ 76c71aae:3e29cafa
2024-08-13 04:30:00On social media and in the Nostr space in particular, there’s been a lot of debate about the idea of supporting deletion and editing of notes.
Some people think they’re vital features to have, others believe that more honest and healthy social media will come from getting rid of these features. The discussion about these features quickly turns to the feasibility of completely deleting something on a decentralized protocol. We quickly get to the “We can’t really delete anything from the internet, or a decentralized network.” argument. This crowds out how Delete and Edit can mimic elements of offline interactions, how they can be used as social signals.
When it comes to issues of deletion and editing content, what matters more is if the creator can communicate their intentions around their content. Sure, on the internet, with decentralized protocols, there’s no way to be sure something’s deleted. It’s not like taking a piece of paper and burning it. Computers make copies of things all the time, computers don’t like deleting things. In particular, distributed systems tend to use a Kafka architecture with immutable logs, it’s just easier to keep everything around, as deleting and reindexing is hard. Even if the software could be made to delete something, there’s always screenshots, or even pictures of screens. We can’t provably make something disappear.
What we need to do in our software is clearly express intention. A delete is actually a kind of retraction. “I no longer want to associate myself with this content, please stop showing it to people as part of what I’ve published, stop highlighting it, stop sharing it.” Even if a relay or other server keeps a copy, and keeps sharing it, being able to clearly state “hello world, this thing I said, was a mistake, please get rid of it.” Just giving users the chance to say “I deleted this” is a way of showing intention. It’s also a way of signaling that feedback has been heard. Perhaps the post was factually incorrect or perhaps it was mean and the person wants to remove what they said. In an IRL conversation, for either of these scenarios there is some dialogue where the creator of the content is learning something and taking action based on what they’ve learned.
Without delete or edit, there is no option to signal to the rest of the community that you have learned something because of how the content is structured today. On most platforms a reply or response stating one’s learning will be lost often in a deluge of replies on the original post and subsequent posts are often not seen especially when the original goes viral. By providing tools like delete and edit we give people a chance to signal that they have heard the feedback and taken action.
The Nostr Protocol supports delete and expiring notes. It was one of the reasons we switched from secure scuttlebutt to build on Nostr. Our nos.social app offers delete and while we know that not all relays will honor this, we believe it’s important to provide social signaling tools as a means of making the internet more humane.
We believe that the power to learn from each other is more important than the need to police through moral outrage which is how the current platforms and even some Nostr clients work today.
It’s important that we don’t say Nostr doesn’t support delete. Not all apps need to support requesting a delete, some might want to call it a retraction. It is important that users know there is no way to enforce a delete and not all relays may honor their request.
Edit is similar, although not as widely supported as delete. It’s a creator making a clear statement that they’ve created a new version of their content. Maybe it’s a spelling error, or a new version of the content, or maybe they’re changing it altogether. Freedom online means freedom to retract a statement, freedom to update a statement, freedom to edit your own content. By building on these freedoms, we’ll make Nostr a space where people feel empowered and in control of their own media.
-
 @ a4a6b584:1e05b95b
2025-01-02 18:13:31
@ a4a6b584:1e05b95b
2025-01-02 18:13:31The Four-Layer Framework
Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
Example: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- Tip: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
Once you have the big picture in mind, it’s time to start breaking it down.
Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
Example: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- Tip: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
With your categories in place, you’re ready to dive into the details that bring them to life.
Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
Example: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- Tip: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
Now that you’ve mastered the essentials, you can expand your knowledge to include extra material.
Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
Example: Learn about rare programming quirks or historical trivia about a language’s development.
- Tip: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
Pro Tips for Better Learning
1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
2. Map It Out
Create visual aids like diagrams or concept maps to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching exposes any gaps in your understanding and helps reinforce the material.
4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to explore your topic in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.Tip: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-
 @ 490b551d:e17f0103
2025-01-02 18:29:07
@ 490b551d:e17f0103
2025-01-02 18:29:07I decided to do a bible study on Romans to get myself back into the Word. Shew. That's a tough place to start for someone who is still working on letting God back in. Right out the gate in Chapter One, there’s a part of it that just doesn’t sit well with me. The more I read, the more I feel like I’m trying to catch my breath, trying to wrap my head around the words Paul wrote. I can't shake the discomfort. I was transported right back into my denial, because I REALLY struggle with the idea of a judgemental God who is supposed to be all-loving.
My Struggle with God's Wrath
Paul writes in Romans 1:18-23 (NLT):
"But God shows his anger from heaven against all sinful, wicked people who suppress the truth by their wickedness. They know the truth about God because he has made it obvious to them. For ever since the world was created, people have seen the earth and sky. Through everything God made, they can clearly see his invisible qualities—his eternal power and divine nature. So they have no excuse for not knowing God. Yes, they knew God, but they wouldn’t worship him as God or even give him thanks. And they began to think up foolish ideas of what God was like. As a result, their minds became dark and confused. Claiming to be wise, they instead became utter fools. And instead of worshiping the glorious, ever-living God, they worshiped idols made to look like mere people and birds and animals and reptiles."
The idea that we should just know that God exists stopped me in my tracks. Paul essentially says that all the beauty around us - nature, the stars, the intricacy of life - should be enough to prove God’s existence to us. That’s heavy. It feels like it puts a burden on our hearts, like we should automatically see all this beauty and immediately recognize God behind it. Even the people who have never been exposed to God, heard of him, have any idea of the Christian version of deity. So what about those people who don’t? What about the times when we miss the beauty or don’t see it the way others do?
And the part I struggle with the most: when people don’t “get it” and worship something other than God, whether that’s idols or nature itself, God is angry. Angry that they looked at creation and created something to worship, but it wasn’t Him. And for the longest time, I couldn’t understand why that was such a big deal. Isn’t it understandable? If you see something beautiful, something life-giving, it’s almost instinctual to try to honor it, right? How could God be mad at people for trying to connect to something bigger than themselves, something so beautiful as nature, especially when they didn’t even have all the information?They're doing the best they can with what they know.
Reading the passage really set me back, because, on the surface, it feels so harsh. So unloving. It feels judgmental. It feels like everything I ran away from ten years ago. And it makes me angry. Angry because it feels unfair that God would be upset at people for trying to reach out with the only tools they had, which were their limited human understanding and the beauty they saw in the world.
The “Invisible God” and the Trap of Human Effort
What really gets me is that the text says God is “invisible." That He can’t be seen or fully known through creation alone. And then, instead of understanding people trying to make sense of that mystery, God gets mad. They looked at the trees, the sky, the mountains, and the oceans, and they gave them credit. They worshiped them, as if nature itself was a god. And, yes, we all know it’s not the right thing to do. But how is that any different than what I’ve seen in my own life where I make mistakes out of ignorance? Does that mean I'm unforgivable?
I think about all the times I’ve felt so lost, searching for meaning, searching for God, trying to figure out what all this beauty around me means. I know deep down that I want to connect with something bigger than me. I want to know unconditional love. If I’m being honest, the natural world has often been the closest I’ve come to feeling connected to God. The mountains, the ocean, a sunset: they all make me feel something deeper, like I’m part of something huge. Something sacred.
But then that verse feels like it’s saying that, instead of leading us to God, the beauty of creation is like a trap. We look at it, we marvel at it, but we miss the point if we don’t see God directly in it. And that confuses me. How can I see beauty and not want to give it honor? How can I feel something so deeply connected to the world around me and still not know God in that moment?
Why Does God Seem So Mad?
This is where the struggle really hits for me. When I read about God’s anger, I feel like it’s more than just disappointment. It's like He’s frustrated that we can’t see through creation and understand Him clearly. And honestly, it feels like I’m being blamed for something I didn’t even know was wrong.
It’s like trying to paint a picture without all the right colors and being told it’s wrong, but never having been given the full palette in the first place. I see people looking at the world, trying to make sense of it, and I can’t help but feel for them. I think, I would’ve done the same thing. If I were in their shoes, how could I have known any better?
After wrestling around this (and an SOS call to my mentor), I came to this conclusion: maybe this is why Jesus had to come. Because we couldn’t see God clearly through the world around us. We couldn’t figure it out on our own. So, God sent Himself, in the form of Jesus, to make it clear. Maybe it’s not that God is mad at us for trying to worship creation. Maybe it’s that we’re worshiping the wrong thing because we don’t fully understand that He’s been there all along, wanting to reveal Himself.
Is God’s Wrath Really About Justice or Separation?
When I sit with this discomfort, I have to remember that God’s wrath in the Bible isn’t about vindictiveness or punishment in the way we often think about it. I’ve come to realize that it’s more about separation. A separation from Him, the source of life, when we choose to worship anything else. It’s not about anger in the way temper-tantrum way I'm picturing, but more about a painful reality of what happens when we go down the wrong path.
We’re choosing to look for answers everywhere except for where they really are. God’s heart is breaking because He knows the only way to true peace and understanding is through Him, but we keep missing it. We’re trying to get back to Him in the best way we know how, but we’re stumbling along the wrong path.
Maybe that’s why that passage feels so heavy. It’s not because God wants to shut us out. It’s because He loves us too much to let us stay lost in our search for meaning. Maybe His anger is a form of sorrow, a sorrow over our inability to see the full picture.
Reaching for God, Even When We Can’t See Him
I think the struggle I feel with this passage is a struggle a lot of people face: how to reconcile that spiritual feeling we get buy maybe don't attribute it to God with the judgment of God, and how to believe that God really loves us when we don’t always know how to connect with Him.
But I’m beginning to see that the beauty of creation is a way that God calls us to Himself, even if it doesn’t feel that way at first. When we worship the world, it’s not that we’re doing something inherently wrong. It’s that we’re just missing the point. God’s anger isn’t His rejection of us. It’s an invitation to look deeper, to see beyond the surface and find the love and the truth that’s been there all along.
I don’t have it all figured out. I still wrestle with passages like these, and I doubt I’ll ever truly “get” God. But I’m learning that God’s love isn’t about always understanding everything perfectly. It’s about trusting that He’s bigger than our confusion, bigger than our doubts, and bigger than our struggle to connect.
Maybe the key isn’t to have all the answers. Maybe it’s to keep seeking, even when we feel like we’re in the dark.
-
 @ 1cb14ab3:95d52462
2025-01-02 05:57:05
@ 1cb14ab3:95d52462
2025-01-02 05:57:05
No. 1 - The Less Touristy "Bund"

The Bund is certainly a must-see if you are traveling to Shanghai for the first time - and it will be at the top of every travel guide out there, for good reason - there are equally as stunning alternatives away from the crowds. If you want to enjoy the skyline from a more relaxed perspective, consider the Pudong side of the river. There are parks, basketball courts, and green spaces along the riverbank for you to chill at and take in the sights. You can also hop on a ferry or a sightseeing boat to cross the river and admire the views from the renowned Bund.
No. 2 - Walks Along Golden Street

This one is out in Gubei, a suburban area in the west of Shanghai. It may be a bit of a trek, but it is worth it if you are looking for a more relaxing and peaceful pedestrian street in the city. Golden Street, or Jinxiu Road, is a great place to walk a dog, grab an afternoon drink, or enjoy a romantic dinner with your loved one. While it may be a bit far from downtown, it makes for a great joyride on your scooter or bicycle.
No. 3 - Moganshan Road Graffiti Wall

Moganshan Road is a gem for all things art. It is home to M50, the best art district in the city, where you will find dozens of galleries, studios, and workshops showcasing a wide range of art. There are also plenty of cool spots scattered around the area, particularly the graffiti wall. The wall is a welcome contrast to some of the drab and monotonous architecture found around the city; with colorful display of street art featuring various styles and themes. Stop by and admire the works of local and international artists, and even jump in to join them in adding your own mark. The wall is constantly evolving, so you can always find something new.
No. 4 - Jiaotong University in the Fall

Easily one of the best spots in town for catching rows of bright yellow and red leaves. Jiaotong University is one of the oldest and most prestigious universities in China. The campus is located in Xuhui District and has a mix of Chinese and Western architectural styles to admire as well. Try to visit in late October or early November for the best leaf-peeping. You can walk along the tree-lined paths, set up a blanket in the field for a picnic, or simply take photos and enjoy the scenery.
No. 5 - Day Drinking at Highline

Hands down one of the top five rooftop bars in the city, along with Bar Rouge, Kartel, and others; Highline is a go-to-spot that offers great views of the city and excellent food. Find it on the sixth floor of the Ascott Hotel in Huaihai Road in Xintiandi. Nothing beats a laid back Saturday afternoon at Highline. I prefer the views during the day, though it is equally as nice a night. Sip cocktails, wine, or beer, and enjoy the music and vibe. Highline is a perfect place to spend an afternoon.
Additional Photos





Next Guide in the Series:
An Expats Guide to the Best Spots in Shanghai: 002
Find Me Elsewhere:
All images property of Hes. Originally published as an Instagram Guide on Feb. 02, 2021. Reworked and published on Nostr on Feb. 17, 2024.
-
 @ ccc8ee23:9f3d9783
2024-12-21 06:38:47
@ ccc8ee23:9f3d9783
2024-12-21 06:38:47Chef's notes
Enjoy these Chocolate Sprinkle Cookies, a delightful combination of buttery richness, velvety chocolate, and a crunchy sprinkle finish
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 90 min
- 🍽️ Servings: 10
Ingredients
- Plain flour 250 grams
- Margarine 100 grams
- Butter 100 grams
- Vanilla essence 1 tsp
- Milk powder 1 tbsp
- Sugar 40 grams
- Chocolate bar - 80 grams, melted
- Chocolate sprinkles - for decoration
Directions
- Make the Dough: Combine the plain flour, margarine, butter, milk powder, sugar, and vanilla essence in a mixing bowl. Knead the mixture by hand until smooth and well combined.
- Shape and divide the dough into small balls, weighing approximately 8 grams each.
- Preheat the oven to 175°C. Arrange the dough balls on a baking tray and bake for about 30 minutes, or until the cookies are dry and fully cooked.
- Coat with Chocolate: Melt the chocolate bar using a double boiler or microwave. Once the cookies have cooled completely, dip each cookie into the melted chocolate, ensuring they are evenly coated.
- Place the coated cookies onto paper cups.
- While the chocolate coating is still wet, sprinkle chocolate sprinkles on top of each cookie.
- Allow the chocolate to dry completely, then arrange the cookies in a decorative airtight container for storage.
-
 @ ccc8ee23:9f3d9783
2024-12-21 06:03:28
@ ccc8ee23:9f3d9783
2024-12-21 06:03:28Chef's notes
Celebrating seasons🎉
Kastengel Chocolate-Dip, where the savoury richness of cheese meets the decadent sweetness of chocolate. A perfect flavours in every bite!
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 90 min
- 🍽️ Servings: 10
Ingredients
- Plain Flour 250 grams
- Margarine - 100 grams
- Butter 100 grams
- Egg yolk 1 pc
- Sugar 20 grams
- Grated cheese 100 grams (half for the dough, half for garnish, adjustable)
- Chocolate bar 80 grams, melted
Directions
- Make the Dough: Combine the plain flour, margarine, butter, sugar, and half of the grated cheese in a bowl. Knead the mixture with your hands until smooth and well incorporated. Roll out the dough using a rolling pin and cut into desired shapes for cookies.
- Beat the egg yolk. Brush the shaped cookies with the egg yolk mixture and sprinkle the remaining grated cheese on top.
- Bake the cookies 175’C for about 30 minutes, or until they are dry and perfectly cooked.
- Melt the chocolate bar in a double boiler or microwave until smooth.
- Dip in Chocolate: Once the cookies have cooled completely, dip both the top and bottom ends of each cookie into the melted chocolate.
- Place the dipped cookies on a wire rack or a cookie drying tray to allow the chocolate to harden and set.
- Arrange the cookies neatly in an airtight container.
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16Drivechain
Understanding Drivechain requires a shift from the paradigm most bitcoiners are used to. It is not about "trustlessness" or "mathematical certainty", but game theory and incentives. (Well, Bitcoin in general is also that, but people prefer to ignore it and focus on some illusion of trustlessness provided by mathematics.)
Here we will describe the basic mechanism (simple) and incentives (complex) of "hashrate escrow" and how it enables a 2-way peg between the mainchain (Bitcoin) and various sidechains.
The full concept of "Drivechain" also involves blind merged mining (i.e., the sidechains mine themselves by publishing their block hashes to the mainchain without the miners having to run the sidechain software), but this is much easier to understand and can be accomplished either by the BIP-301 mechanism or by the Spacechains mechanism.
How does hashrate escrow work from the point of view of Bitcoin?
A new address type is created. Anything that goes in that is locked and can only be spent if all miners agree on the Withdrawal Transaction (
WT^) that will spend it for 6 months. There is one of these special addresses for each sidechain.To gather miners' agreement
bitcoindkeeps track of the "score" of all transactions that could possibly spend from that address. On every block mined, for each sidechain, the miner can use a portion of their coinbase to either increase the score of oneWT^by 1 while decreasing the score of all others by 1; or they can decrease the score of allWT^s by 1; or they can do nothing.Once a transaction has gotten a score high enough, it is published and funds are effectively transferred from the sidechain to the withdrawing users.
If a timeout of 6 months passes and the score doesn't meet the threshold, that
WT^is discarded.What does the above procedure mean?
It means that people can transfer coins from the mainchain to a sidechain by depositing to the special address. Then they can withdraw from the sidechain by making a special withdraw transaction in the sidechain.
The special transaction somehow freezes funds in the sidechain while a transaction that aggregates all withdrawals into a single mainchain
WT^, which is then submitted to the mainchain miners so they can start voting on it and finally after some months it is published.Now the crucial part: the validity of the
WT^is not verified by the Bitcoin mainchain rules, i.e., if Bob has requested a withdraw from the sidechain to his mainchain address, but someone publishes a wrongWT^that instead takes Bob's funds and sends them to Alice's main address there is no way the mainchain will know that. What determines the "validity" of theWT^is the miner vote score and only that. It is the job of miners to vote correctly -- and for that they may want to run the sidechain node in SPV mode so they can attest for the existence of a reference to theWT^transaction in the sidechain blockchain (which then ensures it is ok) or do these checks by some other means.What? 6 months to get my money back?
Yes. But no, in practice anyone who wants their money back will be able to use an atomic swap, submarine swap or other similar service to transfer funds from the sidechain to the mainchain and vice-versa. The long delayed withdraw costs would be incurred by few liquidity providers that would gain some small profit from it.
Why bother with this at all?
Drivechains solve many different problems:
It enables experimentation and new use cases for Bitcoin
Issued assets, fully private transactions, stateful blockchain contracts, turing-completeness, decentralized games, some "DeFi" aspects, prediction markets, futarchy, decentralized and yet meaningful human-readable names, big blocks with a ton of normal transactions on them, a chain optimized only for Lighting-style networks to be built on top of it.
These are some ideas that may have merit to them, but were never actually tried because they couldn't be tried with real Bitcoin or inferfacing with real bitcoins. They were either relegated to the shitcoin territory or to custodial solutions like Liquid or RSK that may have failed to gain network effect because of that.
It solves conflicts and infighting
Some people want fully private transactions in a UTXO model, others want "accounts" they can tie to their name and build reputation on top; some people want simple multisig solutions, others want complex code that reads a ton of variables; some people want to put all the transactions on a global chain in batches every 10 minutes, others want off-chain instant transactions backed by funds previously locked in channels; some want to spend, others want to just hold; some want to use blockchain technology to solve all the problems in the world, others just want to solve money.
With Drivechain-based sidechains all these groups can be happy simultaneously and don't fight. Meanwhile they will all be using the same money and contributing to each other's ecosystem even unwillingly, it's also easy and free for them to change their group affiliation later, which reduces cognitive dissonance.
It solves "scaling"
Multiple chains like the ones described above would certainly do a lot to accomodate many more transactions that the current Bitcoin chain can. One could have special Lightning Network chains, but even just big block chains or big-block-mimblewimble chains or whatnot could probably do a good job. Or even something less cool like 200 independent chains just like Bitcoin is today, no extra features (and you can call it "sharding"), just that would already multiply the current total capacity by 200.
Use your imagination.
It solves the blockchain security budget issue
The calculation is simple: you imagine what security budget is reasonable for each block in a world without block subsidy and divide that for the amount of bytes you can fit in a single block: that is the price to be paid in satoshis per byte. In reasonable estimative, the price necessary for every Bitcoin transaction goes to very large amounts, such that not only any day-to-day transaction has insanely prohibitive costs, but also Lightning channel opens and closes are impracticable.
So without a solution like Drivechain you'll be left with only one alternative: pushing Bitcoin usage to trusted services like Liquid and RSK or custodial Lightning wallets. With Drivechain, though, there could be thousands of transactions happening in sidechains and being all aggregated into a sidechain block that would then pay a very large fee to be published (via blind merged mining) to the mainchain. Bitcoin security guaranteed.
It keeps Bitcoin decentralized
Once we have sidechains to accomodate the normal transactions, the mainchain functionality can be reduced to be only a "hub" for the sidechains' comings and goings, and then the maximum block size for the mainchain can be reduced to, say, 100kb, which would make running a full node very very easy.
Can miners steal?
Yes. If a group of coordinated miners are able to secure the majority of the hashpower and keep their coordination for 6 months, they can publish a
WT^that takes the money from the sidechains and pays to themselves.Will miners steal?
No, because the incentives are such that they won't.
Although it may look at first that stealing is an obvious strategy for miners as it is free money, there are many costs involved:
- The cost of ceasing blind-merged mining returns -- as stealing will kill a sidechain, all the fees from it that miners would be expected to earn for the next years are gone;
- The cost of Bitcoin price going down: If a steal is successful that will mean Drivechains are not safe, therefore Bitcoin is less useful, and miner credibility will also be hurt, which are likely to cause the Bitcoin price to go down, which in turn may kill the miners' businesses and savings;
- The cost of coordination -- assuming miners are just normal businesses, they just want to do their work and get paid, but stealing from a Drivechain will require coordination with other miners to conduct an immoral act in a way that has many pitfalls and is likely to be broken over the months;
- The cost of miners leaving your mining pool: when we talked about "miners" above we were actually talking about mining pools operators, so they must also consider the risk of miners migrating from their mining pool to others as they begin the process of stealing;
- The cost of community goodwill -- when participating in a steal operation, a miner will suffer a ton of backlash from the community. Even if the attempt fails at the end, the fact that it was attempted will contribute to growing concerns over exaggerated miners power over the Bitcoin ecosystem, which may end up causing the community to agree on a hard-fork to change the mining algorithm in the future, or to do something to increase participation of more entities in the mining process (such as development or cheapment of new ASICs), which have a chance of decreasing the profits of current miners.
Another point to take in consideration is that one may be inclined to think a newly-created sidechain or a sidechain with relatively low usage may be more easily stolen from, since the blind merged mining returns from it (point 1 above) are going to be small -- but the fact is also that a sidechain with small usage will also have less money to be stolen from, and since the other costs besides 1 are less elastic at the end it will not be worth stealing from these too.
All of the above consideration are valid only if miners are stealing from good sidechains. If there is a sidechain that is doing things wrong, scamming people, not being used at all, or is full of bugs, for example, that will be perceived as a bad sidechain, and then miners can and will safely steal from it and kill it, which will be perceived as a good thing by everybody.
What do we do if miners steal?
Paul Sztorc has suggested in the past that a user-activated soft-fork could prevent miners from stealing, i.e., most Bitcoin users and nodes issue a rule similar to this one to invalidate the inclusion of a faulty
WT^and thus cause any miner that includes it in a block to be relegated to their own Bitcoin fork that other nodes won't accept.This suggestion has made people think Drivechain is a sidechain solution backed by user-actived soft-forks for safety, which is very far from the truth. Drivechains must not and will not rely on this kind of soft-fork, although they are possible, as the coordination costs are too high and no one should ever expect these things to happen.
If even with all the incentives against them (see above) miners do still steal from a good sidechain that will mean the failure of the Drivechain experiment. It will very likely also mean the failure of the Bitcoin experiment too, as it will be proven that miners can coordinate to act maliciously over a prolonged period of time regardless of economic and social incentives, meaning they are probably in it just for attacking Bitcoin, backed by nation-states or something else, and therefore no Bitcoin transaction in the mainchain is to be expected to be safe ever again.
Why use this and not a full-blown trustless and open sidechain technology?
Because it is impossible.
If you ever heard someone saying "just use a sidechain", "do this in a sidechain" or anything like that, be aware that these people are either talking about "federated" sidechains (i.e., funds are kept in custody by a group of entities) or they are talking about Drivechain, or they are disillusioned and think it is possible to do sidechains in any other manner.
No, I mean a trustless 2-way peg with correctness of the withdrawals verified by the Bitcoin protocol!
That is not possible unless Bitcoin verifies all transactions that happen in all the sidechains, which would be akin to drastically increasing the blocksize and expanding the Bitcoin rules in tons of ways, i.e., a terrible idea that no one wants.
What about the Blockstream sidechains whitepaper?
Yes, that was a way to do it. The Drivechain hashrate escrow is a conceptually simpler way to achieve the same thing with improved incentives, less junk in the chain, more safety.
Isn't the hashrate escrow a very complex soft-fork?
Yes, but it is much simpler than SegWit. And, unlike SegWit, it doesn't force anything on users, i.e., it isn't a mandatory blocksize increase.
Why should we expect miners to care enough to participate in the voting mechanism?
Because it's in their own self-interest to do it, and it costs very little. Today over half of the miners mine RSK. It's not blind merged mining, it's a very convoluted process that requires them to run a RSK full node. For the Drivechain sidechains, an SPV node would be enough, or maybe just getting data from a block explorer API, so much much simpler.
What if I still don't like Drivechain even after reading this?
That is the entire point! You don't have to like it or use it as long as you're fine with other people using it. The hashrate escrow special addresses will not impact you at all, validation cost is minimal, and you get the benefit of people who want to use Drivechain migrating to their own sidechains and freeing up space for you in the mainchain. See also the point above about infighting.
See also
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Personagens de jogos e símbolos
A sensação de "ser" um personagem em um jogo ou uma brincadeira talvez seja o mais próximo que eu tenha conseguido chegar do entendimento de um símbolo religioso.
A hóstia consagrada é, segundo a religião, o corpo de Cristo, mas nossa mente moderna só consegue concebê-la como sendo uma representação do corpo de Cristo. Da mesma forma outras culturas e outras religiões têm símbolos parecidos, inclusive nos quais o próprio participante do ritual faz o papel de um deus ou de qualquer coisa parecida.
"Faz o papel" é de novo a interpretação da mente moderna. O sujeito ali é a coisa, mas ele ao mesmo tempo que é também sabe que não é, que continua sendo ele mesmo.
Nos jogos de videogame e brincadeiras infantis em que se encarna um personagem o jogador é o personagem. não se diz, entre os jogadores, que alguém está "encenando", mas que ele é e pronto. nem há outra denominação ou outro verbo. No máximo "encarnando", mas já aí já é vocabulário jornalístico feito para facilitar a compreensão de quem está de fora do jogo.
-
 @ 2fb77d26:c47a6ee1
2024-12-27 20:12:28
@ 2fb77d26:c47a6ee1
2024-12-27 20:12:28John Brockmans Edge-Foundation galt als Treffpunkt für die Genies der Gegenwart. Ob Jeff Bezos, Sean Parker, Elon Musk oder Daniel Hillis – sie alle wohnten Veranstaltungen bei, die sie als Tech-Avantgarde darauf vorbereiten sollten, die Zukunft zu gestalten. Die »Dritte Kultur«. Doch was zunächst progressiv klingt, entpuppt sich auf den zweiten Blick rasch als Trainingslager für Technokraten. Finanziert von Jeffrey Epstein.
Original mit Quellen (VÖ: 24.11.2024) - https://www.regenauer.press/die-glorreichen-sieben
Sie regieren die Welt. Das ist keine Übertreibung. Denn sie haben deutlich mehr Einfluss darauf, was wir sehen, lesen, hören, fühlen, kaufen, tun und denken als jeder Politdarsteller – gemeint sind die »glorreichen Sieben«. Also die sieben größten Unternehmen der Tech-Branche: Apple, Microsoft, Amazon, Alphabet (Google), Tesla, Meta und Nvidia. Mit ihren Plattformen, Produkten und Smartphone-Apps dominieren sie Medienlandschaft, Konsum, persönliche Kommunikation, digital-soziale Räume, nachrichtendienstliche Aktivitäten, künstliche Intelligenz (KI) und in zunehmendem Maße auch den Finanzmarkt.
Nachdem Microsoft und Apple mit der Entwicklung von Personal Computern und einer grafischen Benutzeroberfläche dafür sorgten, dass sich Mitte der 80er auch neugierige Normalos einen PC ins Haus holten – als Ersatz für die plötzlich altbacken wirkende Schreibmaschine – und Tim Berners-Lee, der 1989 am CERN die Grundlagen des World Wide Web entwickelte, am 6. August 1991 sein Konzept eines Hypertext-Dienstes online gestellt hatte, waren es Ende der 90er eine Handvoll Unternehmen, die sich im sonnigen Süden der USA anschicken sollten, das Mediazän zu dominieren. Gegründet von einer Handvoll Tech-Desperados, die abseits gültiger Normen und Gesetzmäßigkeiten operierte, weil es für das, was sie erfanden, noch keine gab, formierte sich ein anomistisches Ökosystem, das heute die Welt dominiert: Die Plattform-Plutokratie. Der digital-zensorische Komplex. Die größte Social-Engineering-Maschinerie aller Zeiten.
So steht die Einordnung als »größte Unternehmen« nicht nur für die astronomischen Börsenwerte dieser Konzerne, sondern vor allem für ihren massiven Einfluss auf die Entwicklung des Individuums und die postmoderne Gesellschaft an sich. Dass diese Einflussnahme abseits von Marktwert und Performance-Indikatoren nicht allein auf organischem Wachstum und Marktdurchdringung beruht, liegt auf der Hand – denn die Tech-Giganten erfuhren signifikante Starthilfe von Seiten des Staates. Genauer gesagt dem Geheimdienstkomplex.
Facebook erhielt Millionen von Deep-State-Technokrat Peter Thiel und Accel, dessen Management enge Verbindungen zum CIA-Finanzvehikel In-Q-Tel pflegte, und galt für das Forbes-Magazine schon 2018 als »das ultimative Überwachungsinstrument für Regierungen«. Sergey Brin und Larry Page erhielten 1995 erhebliche Summen von der DARPA, um Google zu gründen. Aus einem »schwarzen Budget«, mit dem NSA und CIA Werkzeuge zur Massenüberwachung entwickeln wollten. Wenig verwunderlich also, dass auch Google Earth aus einem CIA-Projekt namens Keyhole EarthViewer hervorging, dessen Unterstützung In-Q-Tel gemäß Pressemitteilung vom 25. Juni 2003 als »strategisches Investment« bezeichnete. Julian Assange lag also ganz richtig, als er 2014 warnte, »Google sei nicht das, für was es sich ausgibt«.
Selbst bei Reuters konnte man im Rahmen eines ausführlichen Artikels vom 3. Juli 2013 nachlesen, wie eng die Verbindungen der Big-Tech-Konzerne zu Geheimdiensten ist. Von der Start-up-Finanzierung über die Rekrutierung von Ex-Agenten bis zum Austausch von Computerchips, die Spionage erleichtern, ist alles dabei. »Die Zusammenarbeit zwischen Tech-Industrie und Geheimdiensten ist enger als die meisten Menschen denken«, so Reuters.
So erstaunt es kaum, dass Amazon, Apple, Microsoft, Google, Meta und Elon Musks Firmenkonglomerat mittlerweile auch in den Krisen- und Kriegsgebieten der Welt aktiv sind, um dort in Zusammenarbeit mit Peter Thiels Palantir, Pentagon und Geheimdiensten jene Drecksarbeit zu übernehmen, die Regierungen nicht offiziell übernehmen wollen, oder dürfen. Korporatismus in voller Blüte eben. Die vermeintlich privatwirtschaftlich geführten Tech-Konzerne dominieren nicht mehr nur den zivilen, sondern zusehends auch den militärischen »Markt« – das Geschäft des industrialisierten Tötens.
Dass der militärisch-industrielle mit dem digital-zensorischen Komplex fusionierte, ist eine logische Folge des Umstands, dass beide dem gleichen »Gott« dienen: Mammon. Sprich, dem Zentral- und Geschäftsbankenkartell. In diesem Lichte betrachtet gebietet das Gesetz der Logik, dass die Schaffung dieser unheiligen Allianz nicht allein betriebswirtschaftlich motiviert war. Denn schon im 17., 18., und 19. Jahrhundert nutzten die Finanzkartelle Medien, Staat und Wirtschaft, um den Lauf der Dinge zu ihren Gunsten zu beeinflussen. Siehe mein Text »Monopole, Macht und Mord« Teil 1 und 2.
Damals zeitigte diese überstaatliche Einflussnahme vor allem militärische Konflikte, bei denen Territorialansprüche, Ressourcen und Monopolisierung im Fokus standen. Weil in diesen Bereichen aber bis auf die planetaren Gemeingüter, die sich die Herrschaftskaste nun im Rahmen der Green Economy unter den Nagel zu reißen gedenkt, nicht mehr viel zu holen ist, geht es dieser Tage vor allem darum, die Kontrolle nicht zu verlieren. Dazu müssen die 0,1 bis 1,0 Prozent an der Spitze des wertewestlichen Kastensystems sicherstellen, dass die unterworfene Masse der transgenerational operierenden Kriminalität ihrer Zirkel nicht auf die Schliche kommt.
Eine Bedrohung für die von immer mehr Rissen gezeichneten Fundamente des Elfenbeinturms markiert vor allem das Internet. Denn trotz vielschichtiger Zensurmethoden im Web 2.0, legislativer Hütchenspielertricks und der Segregation Andersdenkender, bahnt sich das kleine, aber persistente Licht der Wahrheit auch in dunkelsten Zeiten seinen Weg durch Paywalls, Geofences, Blockwart-Barrikaden und Plattform-Patrouillen. VPN, Blockchain, Graphene OS, De-Fi (Decentralized Finance) und Verschlüsselung sei Dank. Das Web 3.0 lässt sich nicht zensieren.
Um derart autonomisierenden Entwicklungen entgegenzuwirken, konzentrieren sich die Kolonialisierungsprojekte der Herrschaftskaste nun nicht mehr auf die bewaffnete Unterwerfung ferner Länder – sondern auf das Erringen der Lufthoheit über einem geradezu grenzenlosen Schlachtfeld: dem Gehirn. Allerdings nicht in Form simpler Propaganda. Denn im Zeitalter des fortgeschrittenen Informationskrieges ist Nudging die sozialarchitektonische Königsdisziplin, um Menschen dazu zu bringen, etwas zu unterstützen, das ihnen nichts bringt, oder sogar schadet. Und wie könnte Nudging in der Breite besser gelingen als durch willfährige Hilfestellung »der glorreichen Sieben«. Genau dazu wurden sie geschaffen.
Technologische Revolutionen werden Dekaden bevor sie eintreten antizipiert, durchdacht, angekündigt und visualisiert. Nicht zuletzt von Hollywood, der laut Edward Bernays »größten Propagandamaschine der Welt«. Jene Kräfte, die die Gesellschaft kontrollieren wollen, machen sich das zu nutze. Sie erkennen, welche Paradigmenwechsel technologische Revolutionen einläuten werden und versuchen daher frühzeitig, deren Entwicklung zu steuern. Aus diesem Grund lohnt sich ein Blick auf die Entstehungsgeschichte des Nudging – beziehungsweise der zugrundeliegenden wissenschaftlichen Disziplin: Verhaltensforschung.
Klassische Propaganda beruht auf den Standardwerken von Walter Lippmann (1922) und Edward Bernays (1928). Moderne Verhaltensforschung – oder Sozialarchitektonik – in weiten Teilen auf den Arbeiten von Anthony Giddens. Der britische Soziologe veröffentlichte 1990 das Buch »The Consequences of Modernity«, in dem er die Grundlagen für den »Dritten Weg« skizzierte – ein Konzept der Politikproduktion, das abseits politischer Spektren dazu dient, die Massen zu gesellschaftlichem Konsens zu zwingen. Giddens’ Konzept beruht auf den Infiltrationsansätzen der Fabian Society, die damit das Fundament der Partizipation simulierenden Sozialdemokratien des heutigen Europas schuf. Hintergründe zu Fabian Society und dem Roll-out des Dritten Weges finden sich in meinem Text »Dominanzdialektik« vom 30. September 2023.
Nach 1990 publizierte Giddens weitere Bücher, die sich mit dem Themenkomplex befassten. Darunter Titel wie »Moderne und Identität« (1991), »Die Transformation der Intimität« (1992), »Jenseits von rechts und links« (1994) und »Der Dritte Weg« (1998). In all diesen Werken beschäftigt sich der Sozialwissenschaftler mit der übergeordneten Frage, wie der Mensch sich in die Welt der Postmoderne einzufügen vermag – oder besser – einfügen muss, um mit Globalisierung, Klimawandel und sozialen Verwerfungen zurecht zu kommen. Anthony Giddens war von 1997 bis 2003 Direktor der einflussreichen, von der Fabian Society gegründeten London School of Economics. Er ist der meistzitierte Autor im Bereich soziologischer Studien und Mitglied des 2007 ins Leben gerufenen European Council on Foreign Relations.
Relevant ist Giddens Arbeit zum »Dritten Weg« vor allem deshalb, weil dieser manipulative Ansatz der Politikproduktion durch Tony Blair, Bill Clinton und Gerhard Schröder Einzug in die Parlamente des Wertewestens fand. Heute orientiert sich praktisch jede Regierung an Giddens Theorien – und setzt demzufolge um, was die Fabian Society bereits Ende des 19. Jahrhunderts vorschlug, um Kollektivismus unter dem Deckmantel von Mitbestimmung zu generieren. Das erklärt, warum weder Klaus Schwabs »Stakeholder Kapitalismus« noch die »Vierte Industrielle Revolution« etwas mit Kapitalismus oder Demokratie zu tun haben.
Damit solche Konzepte in der Gesellschaft Fuß fassen, benötigt es vor allem eine auf Linie gebürstete Führungsebene. Diese wird mit Stipendien und Förderprogrammen eingenordet, bevor man sie auf die Bevölkerung loslässt. Viele dieser Kaderschmieden sind mittlerweile hinlänglich bekannt. Da wäre zum Beispiel das zu fragwürdigem Ruhm gelangte Young Global Leaders Programm des Weltwirtschaftsforums (WEF), das neben knapp 3.800 weiteren Absolventen auch Angela Merkel, Tony Blair, Gordon Brown, Nicolas Sarkozy und Bill Gates auf ihre Karrieren in der »regelbasierten internationalen Ordnung« vorbereitete. Ein weiterer WEF-Absolvent ist Lawrence Summers, US-Finanzminister unter Bill Clinton, nationaler Wirtschaftsberater unter Barack Obama und von 1991 bis 1993 Chefökonom der Weltbank. Darüber hinaus war Summers von 2001 bis 2006 Präsident der Harvard University, wo bis 2006 auch Mark Zuckerberg studierte und mit drei Kommilitonen Facebook gründete.
Nach nicht zweifelsfrei verifizierbaren Angaben eines anonymen Facebook-Whistleblowers soll Summers in diesem Zeitraum auf Zuckerberg zugegangen sein, um ihm für die Mitarbeit an einem Social-Media-Überwachungs-Projekt der DARPA lukrative Regierungsaufträge in Aussicht zu stellen – siehe Life Log, das einen Tag vor dem Start von TheFacebook offline ging. In Anbetracht von Summers Position durchaus denkbar. Auch Moral scheint dem Mann ein Fremdwort zu sein, wie Formulierungen aus einem Weltbank-Memo Summers zeigen, die am 18. Mai 1993 bei einer Anhörung im US-Senat thematisiert wurden.
»Ich denke, die wirtschaftliche Logik, die hinter der Entsorgung einer Menge von Giftmüll in einem Land mit den niedrigsten Löhnen steht, ist einwandfrei, und wir sollten uns dem stellen. (…) Ich war schon immer der Meinung, dass die unterbevölkerten Länder Afrikas stark unterverschmutzt sind.«
Nicht zu vergessen Summers enge Verbindungen zum Pädophilen, Sexualstraftäter und Menschenhändler Jeffrey Epstein. Nachdem Summers bereits mehrfach mit Epsteins Privatjet – bekannt unter dem Namen »Lolita Express« – unterwegs war, bestieg er die Maschine nur zehn Tage nach seiner Hochzeit im Jahr 2005 erneut, um Epsteins ominöse Privatinsel »Pedophile Island« zu besuchen. Die Huffington Post schrieb dazu am 24. April 2020: »Joe Biden sollte sich von Larry Summers fernhalten – Summers ruiniert alles, was er anfasst«. Summers WEF-Training scheint sich jedenfalls ausgezahlt zu haben. Denn wer mit Jeffrey Epstein zu tun hatte, ist definitiv im Establishment angekommen.
Tony Blair und Gordon Brown hatten vor dem WEF bereits das 1940 von Nelson Rockefeller initiierte und bis heute vom US-Außenministerium betriebene »International Visitor Leadership Program« (IVLP) durchlaufen. Auch der 1972 gegründete German Marshall Fund betreibt diverse Förderprogramme – siehe EU-US Young Leaders Seminar 2024 oder Policy Designers Network 2024, das sich auf transatlantisch bewegten Nachwuchs aus der Ukraine, Georgien und Armenien fokussiert. Auch die Elite-Universitäten kümmern sich um Nachwuchs. So unter anderem das seit 1902 bestehende Rhodes Stipendium der Oxford-Universität, das neben unzähligen US-Senatoren, Finanzmagnaten, Bestsellerautoren und Wissenschaftlern beispielsweise Edwin Hubble, Bill Clinton oder Naomi Wolf zu Ruhm verhalf. Rhodes-Alumni bleiben über Organisationen wie AARS (Association of American Rhodes Scholars) ein Leben lang verbunden.
Diesbezüglich Fakten zusammenzutragen erscheint bisweilen müßig. Denn mit Details und Verflechtungen zu Entitäten dies- und jenseits des Atlantik, die Führungskräften von morgen die sozioökonomische Philosophie der Herrschaftskaste vermitteln, könnte man Bände füllen. Versucht man die Herrschaftsphilosophie der heutigen Plattform-Plutokraten zu verstehen, sticht eine Organisation dabei allerdings heraus – und zwar die 1988 von John Brockman ins Leben gerufene Edge Foundation. Geburtsort der »Dritten Kultur«.
Die Frankfurter Allgemeine portraitierte Brockman am 7. Januar 2014 mit den einleitenden Worten: »Der wohl wichtigste Buchagent der Welt versammelt in seinem Internetsalon Edge die Cyber-Elite.« Danach beschreibt FAZ-Autor Jordan Mejas, was sich der Normalsterbliche unter Edge vorstellen darf:
»Edge, das ist der Treffpunkt für die Cyber-Elite, die erlauchtesten Geister, die das Vorfeld der neuesten natur- und sozialwissenschaftlichen Entwicklungen prägen, ob nun digital oder gentechnisch, ob psychologisch, kosmologisch oder neurologisch. Jedenfalls melden sich bei Brockman nicht nur Digerati aus dem Computeruniversum des Silicon Valley zu Wort, sondern genauso häufig Koryphäen wie die Evolutionsbiologen Richard Dawkins und Steven Pinker, der Philosoph Daniel Dennett, der Kosmologe Martin Rees, die biologische Anthropologin Helen Fisher, der Ökonom, Psychologe und Nobelpreisträger Daniel Kahneman, der Quantenphysiker David Deutsch, der Computerwissenschaftler Marvin Minsky oder der Sozialtheoretiker Anthony Giddens. Vom Apple-Mitbegründer Steve Wozniak bis zum Genomentschlüssler Craig Venter reicht seine Gästeliste, die ihresgleichen auch in der grenzenlosen Weite des Internets kaum finden wird.«
Was dem FAZ-Autor bei seiner Recherche offensichtlich entging, ist, dass neben Giddens, Wozniak, Dennis Hopper und all den wissenschaftlichen Koryphäen auch Jeff Bezos (Gründer von Amazon, Besitzer Washington Post), Elon Musk, Sean Parker (Gründer von Napster, Co-Gründer Facebook), Larry Page und Sergey Brin (Gründer von Google), Pierre Omidyar (Gründer von eBay), Salar Kamangar (ehem. CEO YouTube), Matt Groening (Erfinder von »Die Simpsons«), Marissa Mayer (ehem. CEO Google und Yahoo), Joi Ito (ehem. Direktor MIT Media Lab), Evan Williams (Co-Gründer Twitter), Paul Romer (Economist) oder Bill Gates regelmäßig auf der Gästeliste von Edge-Events standen. Wer sich durch die Event-Sektion der Edge-Webseite klickt, begegnet unter dem Menüpunkt »Billionaires’ Dinner« der damaligen wie heutigen Crème de la Crème der Plattform-Plutokratie. Garniert mit ein paar Sahnehäubchen aus Wissenschaft, Kunst und Kultur.
Hervorzuheben ist dabei vor allem das Billionaires’ Dinner 2011. Denn die Fotogalerie des Events (hier zusätzlich gesichert im Internet Archive) birgt eine kleine Überraschung: das bislang einzige Foto, das Elon Musk in Gegenwart des zu diesem Zeitpunkt bereits für Sexualstraftaten und Menschenhandel angeklagten Jeffrey Epstein zeigt. Musk sitzt zwar am Nebentisch, mit dem Rücken zur Kamera, ist dank Vergleichsaufnahmen des Events aber zweifelsfrei zu identifizieren. Interessant ist dieser Umstand deshalb, weil Musk bisher stets behauptete, Epstein lediglich einmal in dessen Haus in New York getroffen zu haben. Für 30 Minuten. Und zwar auf Drängen seiner damaligen Partnerin Talulah Riley, die Epstein angeblich für ihre Arbeit an einer Novelle kennenlernen wollte.
Ein Artikel der Newsweek vom 9. November 2022 bestätigt sowohl Musks als auch Epsteins Anwesenheit beim Edge Billionaires’ Dinner 2011. Darüber hinaus geht Newsweek noch einmal auf den Umstand ein, dass Elon Musk bereits auf einem Foto von 2014 mit Ghislaine Maxwell zu sehen war, der linken und rechten Hand Epsteins. Musk gab an, dass besagtes Bild nur entstanden sei, weil Maxwell sich ungefragt ins Bild gedrängt habe. Diesen Eindruck macht das Foto zwar nicht, das Gegenteil zu beweisen, dürfte jedoch schwer fallen. Nun sind Fotos von Gästen einer Veranstaltung natürlich noch kein Beleg dafür, dass sie mit deren Organisation zu tun haben. Finanzielle Zuwendungen dagegen schon.
Entsprechend bedeutsam ist daher ein Artikel der BuzzFeed News vom 27. September 2019. Denn er belegt, dass der bei Weitem größte Einzelspender der Edge-Foundation kein Geringerer war als Jeffrey Epstein. Das veranschaulichen die von ProPublica veröffentlichten Steuerunterlagen von Brockmans »Internetsalon« für 2001 bis 2017. So spendete Epstein 638.000 US-Dollar – während die gesamten Spendeneinnahmen sich auf 857.000 US-Dollar beliefen. Ein eigenes Profil auf der Edge-Webseite hatte Epstein natürlich auch. Kaum verwunderlich also, dass die Edge-Foundation ihre wichtigste jährliche Veranstaltung – das Billionaires’ Dinner – sofort einstellte, nachdem Epsteins Zuwendungen ab 2016 ausblieben. BuzzFeed News führt diesbezüglich aus:
»Epstein war ein regelmäßiger Teilnehmer bei Edge-Veranstaltungen. Er war bei den Billionaires’ Dinner Events 1999 und 2000 auf Fotos und Seiten zu sehen, die kürzlich von der Edge-Website gelöscht wurden, und wurde auch in einem Bericht über das Abendessen 2004 erwähnt. Epstein war auch 2011 bei Edge-Veranstaltungen anwesend, nach seiner Verurteilung wegen Sexualverbrechen im Jahr 2008. Darüber berichtete BuzzFeed News Anfang dieses Monats.«
Überschrift des betreffenden Artikels: »2011 war Jeffrey Epstein ein bekannter Sexualstraftäter. Jeff Bezos, Elon Musk und Sergey Brin speisten trotzdem mit ihm.« Weiter erklärt BuzzFeed:
»2002 waren Brockman, seine Frau und Geschäftspartnerin Katinka Matson sowie die führenden Wissenschaftler Steven Pinker, Richard Dawkins und Daniel Dennett in Epsteins Jet auf dem Weg zu TED in Monterey, Kalifornien, zu sehen – der mehrtägigen Technologie-, Unterhaltungs- und Designkonferenz, bei der das Billionaires’ Dinner diesen Jahres stattfand. Die Bildunterschrift wurde kürzlich geändert, um die Erwähnung Epsteins zu entfernen. Sein Edge-Profil, das ihn als Finanzier und Wissenschaftsphilanthrop beschreibt, wurde ebenfalls entfernt. Ob Epstein selbst am Billionaires’ Dinner 2002 teilnahm, ist unklar. Aber Mitglieder seines Gefolges waren dort. Ein Foto von der Veranstaltung zeigt Brockman mit zwei jungen Frauen, die in der Bildunterschrift namentlich genannt werden. Das Foto wurde kürzlich ebenfalls von der Edge-Webseite entfernt. Eine dieser Frauen ist Sarah Kellen, die als Assistentin von Epsteins ehemaliger Freundin Ghislaine Maxwell angestellt und im Rahmen eines Vergleichs von 2008 vor Strafverfolgung geschützt war. Der Vergleich brachte Epstein nach seiner früheren Verhaftung eine 13-monatige Gefängnisstrafe in Florida ein. In mehreren Klagen haben Epsteins Opfer behauptet, Kellen gehöre zu den Personen, die halfen, den sexuellen Missbrauch für Epstein zu organisieren.«
Brockmans Interaktionen mit Epstein gingen aber offenbar weit über die Edge-Foundation hinaus. Im August 2019 publizierte der belarussische Publizist Evgeny Morozov auf Google Drive E-Mail-Korrespondenz aus dem Jahr 2013, die belegt, dass Brockman Pläne hatte, ein Meeting zwischen ihm und Epstein zu arrangieren. Doch Morozov lehnte ab. In den Mails an Morozov erwähnt Brockman Epsteins »hübsche junge Assistentin aus Weißrussland« und beschreibt seinen Gönner fälschlicherweise als »Milliardär, dem Victorias Secret und eine Modelagentur gehören«. Tatsächlich lag Epsteins Vermögen gemäß seines Testaments aber nur bei einigen hundert Millionen – und die fragwürdige Marke Victorias Secret ist Teil von L Brands, der Holding von Leslie Wexner, einem Tiefenstaat-Veteran mit Verbindungen zu Harvard und WEF-Gründung, dessen Finanzen Jeffrey Epstein bis 2007 verwaltete.
Auch sonst pflegte Brockmans Organisation verwunderliche Geschäftspraktiken. Zwischen 2001 und 2017 vergab die Edge-Foundation beispielsweise nur ein einziges Mal einen Förderpreis. Der entsprechende Betrag in Höhe von 100.000 US-Dollar ging an David Deutsch, einen Pionier für Quanteninformationstheorie, der an der Universität Oxford forschte. Financier des Preises – man ahnt es – war Jeffrey Epstein. Nicht umsonst stellte The Verve am 19. September 2019 fest, dass »Jeffrey Epstein die Wissenschaft infiltrierte, weil die Wissenschaft bereit war, ihn willkommen zu heißen«.
So knüpfte der Finanzmagnat Kontakte zu prominenten Biologen wie George Church, weil er nach Wegen suchte, die menschliche Spezies mit seiner DNA zu kreuzen. Langfristiges Ziel: Das Schaffen einer »Super-Rasse«. Mehrere preisgekrönte Wissenschaftler bestätigten gegenüber der New York Times, dass Epstein auch sie in seine misogynen Pläne eingeweiht hatte. Auf seiner abgelegenen, unterkellerten »Zorro-Ranch« in New Mexico, wo jedes Zimmer mit Kameras überwacht wurde, hatte er eigens ein Behandlungszimmer einrichten lassen, um künstliche Befruchtungen mit jungen Frauen durchführen zu können.
Bei The New Yorker konnte man am 6. September 2019 nachlesen, dass Epstein sich auch im Bereich digitale Währungen engagierte. Unter anderem finanzierte er das damals von Joi Ito geleitete MIT Media Lab – und damit auch die von Ito geführte Digital Currency Initiative (DCI). Diese wiederum unterstützte die Bitcoin-Core-Entwickler bei der Fork 2017, die Bitcoin von einer digitalen Währung zu, wie Epstein es nannte, »digitalem Gold« machen sollte – und damit weitaus ungefährlicher für das herrschende Finanzmarktkartell. Bill Gates, Harvard-Autoren wie Steven Pinker oder MIT-Programmierer wie Richard Stallmann verteidigten Epstein sogar noch nach dessen endgültiger Festnahme. Stallmann forderte gar, Kinderpornografie zu entkriminalisieren. Joi Ito dagegen kündigte kleinlaut beim MIT. Heute ist er Präsident des Chiba Institute for Technology in Japan, wo das Center for Radical Transformation (CRT) angesiedelt ist. Auch die Digital Currency Initiative gibt es bis heute. Genau wie das »digitale Gold«, mit dem aber fast niemand mehr bezahlt. HODL und so.
Mit dem Thema Digitalwährungen nähern wir uns denn auch Jeffrey Epsteins Einfluss auf den Geschäftsbereich der »glorreichen Sieben«. Denn der im Gefängnis ermordete Menschenhändler finanzierte nicht nur einen Großteil von Brockmans Edge-Aktivitäten, sondern sorgte durch die Infiltration des Wissenschaftsbetriebes auch dafür, dass Edge den Tech-Nachwuchs in genau der Domäne schulte, die für das Erringen von Weltherrschaft im Mediazän essenziell ist: Social Engineering.
Dazu veranstaltete die Edge-Foundation sogenannte Master Class Events. Im Jahr 2008 zum Beispiel zum Thema »Libertärer Paternalismus – warum es nicht möglich ist, nicht zu nudgen«. Dozent: Richard Thaler, »Vater der modernen Verhaltensökonomie«, über den die ZEIT am 18. Mai 2010 unter der Überschrift »Die Stunde der Verführer« schrieb:
»Richard Thaler hat den Draht nach oben. Der 64-Jährige ist einer der weltweit führenden Verhaltensökonomen – neuerdings berät er auch die Wirtschaftsexperten des mächtigsten Mannes der Welt, US-Präsident Barack Obama. Auch die britischen Konservativen, die in London die neue Regierung führen, haben dem Professor der Universität von Chicago einen Beraterposten versprochen. Thaler steht an der Spitze einer wirtschaftspolitischen Revolution. (…) Verhaltensorientierte Wirtschaftsforscher postulieren (…) eine grundlegend andere Wirtschaftspolitik. Zwar lehnen sie – ähnlich wie klassische liberale Ökonomen – eine direkte Bevormundung des Einzelnen durch den Staat ab. Sie sprechen sich aber für sanften Druck aus, mit dem der Staat die Menschen in die richtige Richtung leitet, ihnen gleichzeitig aber die Option lässt, sich anders zu entscheiden, wenn sie es wollen. »Nudge« (Anstupsen) hat Thaler dieses Politikkonzept zusammen mit Co-Autor Cass Sunstein im gleichnamigen Buch getauft. Private Institutionen, Behörden und Regierungen versuchen dabei, die Entscheidungen der Menschen so zu lenken, dass sie hinterher besser dastehen. Ein anderer Begriff, der den neuen Politikansatz charakterisiert, ist sanfter Paternalismus.«
Das Buch, das ZEIT-Autor Olaf Storbek referenziert, hat Thaler 2010 gemeinsam mit Cass Sunstein verfasst, einem Edge-Kollegen und Harvard-Professor für Rechtswissenschaft und Verhaltensökonomie. Deutscher Titel des Werks: »Nudge – wie man kluge Entscheidungen anstößt«. Alternativ untertitelt mit: »Wie man Menschen dazu bringt, das Richtige zu tun«. In welche Kerbe das Machwerk schlägt, zeigt der Umstand, dass Cass Sunstein schon im Januar 2008 ein Papier namens »Verschwörungstheorien« publizierte, die er darin als ernsthaftes Risiko für Recht und Gesetz einstufte. Sunstein verteidigt das offizielle 9/11-Narrativ, will eine bargeldlose Gesellschaft und hielt Corona-Lockdowns für eine »smarte« Sache. Ein Beitrag von Sunstein für »Educators at Home« vom 14. September 2010 offenbart, was für ein Menschenbild die Rechtswissenschaften in Harvard mittlerweile kultivieren:
»Wenn wir erst einmal wissen, dass Menschen menschlich sind und etwas von Homer Simpson in sich tragen, dann kann man viel tun, um sie zu manipulieren.« (Cass Sunstein)
Trotz, oder gerade wegen dieser respektlosen Haltung gegenüber den Freiheitsrechten des Individuums, öffnete ihr gemeinsames Werk Thaler und Sunstein die Türen zum Elfenbeinturm. Ab 2008 berieten die beiden Verhaltensökonomen die Regierung von Barack Obama beim Aufbau sogenannter »Nudge-Units«. Kurze Zeit später unterstützte Richard Thaler auch die britische Regierung und half bei der Formierung des »Behavioural Insights Team« (BIT), dem sowohl Sunstein als auch Thaler bis heute angehören. Das BIT spielte via SAGE (Scientific Advisory Group for Emergencies), dem britischen Äquivalent zum Robert-Koch-Institut (RKI), eine tragende Rolle bei der Implementierung der Covid-19-Maßnahmen in Großbritannien. Händewaschanleitungen für Erwachsene, tote Großeltern für die Kleinen. Sie wissen schon. Strategieberater von Tony Blair hatten bereits im Februar 2004 eine Studie zum Thema »Persönliche Verantwortung und Verhaltensänderung: Stand des Wissens und Auswirkungen auf die öffentliche Politik« erstellen lassen – nur Thalers griffige Bezeichnung für die neue Doktrin fehlte noch. Ein Auszug aus dem Papier von 2004 erklärt:
»Mit Blick auf die Zukunft besteht ein offensichtlicher Bedarf, unser theoretisches und empirisches Verständnis der Ursachen für Verhalten und Verhaltensänderung zu stärken. Ebenso wichtig wird die umfassendere Erprobung politischer Instrumente sein, um ein ausgefeilteres Instrumentarium für politische Entscheidungsträger zu entwickeln. Die Politik sollte nicht einfach persönliche Verantwortung oder Schuldzuweisungen proklamieren, sondern muss sich an der Art und Weise orientieren, wie Menschen tatsächlich denken und fühlen, sowie an den sozialen und psychologischen Kräften, die das Verhalten beeinflussen.«
Das war vor 20 Jahren. Drei Jahre später kam das Smartphone auf den Markt und mauserte sich binnen kurzer Zeit zum perfekten Werkzeug einer auf Nuding ausgelegten Observationsökonomie. Heute hat fast jeder ein grell illuminiertes Brett vor dem Kopf, das seinen Tagesablauf, Bio-, Kommunikations- und Schlafrhythmus beeinflusst. Oder steuert. Je nach Schwere der Handysucht. Das eigentliche Problem dabei ist jedoch nicht die Hardware, das Endgerät, sondern die Software der »glorreichen Sieben«. Denn sie ist so designt, dass sie abhängig, krank und depressiv macht – und Menschen dazu bewegt, »das Richtige zu tun«. Auch wenn es absolut falsch ist.
»Wie schaffen wir es, möglichst viel von deiner Zeit und Aufmerksamkeit zu konsumieren. Dazu müssen wir dir hin und wieder eine kleine Dopamin-Dosis verabreichen. (...) Das bringt dich dazu, mehr beizutragen, was dir wiederum mehr Kommentare und Likes bringt. Es ist ein sozial validierender Feedback-Loop. (...) Wir nutzen eine Schwäche der menschlichen Psychologie. Die Erfinder, die Erschaffer, ich, Mark, die Leute von Instagram, all diese Menschen, haben das verstanden - voll und ganz - und wir haben es trotzdem getan.« (Sean Parker, am 8. November 2017)
Nahtlos kontrolliert wird der auf Konformismus dressierte Bürger dabei von einem Überwachungskomplex unvorstellbaren Ausmaßes. Die Webseite von Surveillance Watch führt Buch über die wichtigsten dafür zuständigen Unternehmen.
Nachdem Facebook 2004 online ging und das iPhone 2007 auf den Markt kam, erscheint das Jahr 2008 also tatsächlich als der perfekte Zeitpunkt für Edge, um die Silicon-Valley-Elite in puncto Nudging und Sozialarchitektonik zu schulen. Das soziale Netzwerk war seinen Kinderschuhen entwachsen – am 26. August 2008 knackte Facebook die 100 Millionen-Nutzer-Marke – und mit dem Taschenspion aus dem Hause Apple kündigte sich bereits das mächtigste Manipulations-Malträtat der Zivilisationsgeschichte an. Für die herrschenden Zirkel war absehbar, dass die Frontlinien des transgenerationalen Informationskrieges schon bald nicht mehr über die Auslagen der Zeitungskioske, durch Rundfunkredaktionen oder über die Mattscheibe, sondern direkt durch die Köpfe der Bevölkerung verlaufen werden.
Dieses Ziel wurde fraglos erreicht. Entsprechend hellhörig sollte machen, welche Themen die Edge Master Class 2008 behandelte. Die zweite Session widmete sich zum Beispiel dem Thema »Verbesserung der Auswahlmöglichkeiten durch maschinenlesbare Offenlegung«. Richard Thaler umriss deren Inhalt mit folgendem Eröffnungsstatement.
»Das ist die Idee. Ich nenne es elektronische Offenlegung. Lassen sie mich erklären, wie es bei Kreditkarten funktionieren würde. Die Idee ist, dass das Kreditkartenunternehmen ihnen für jede Kreditkarte, die sie besitzen, einmal im Jahr zwei elektronische Dateien senden muss. Die erste Datei wäre im Wesentlichen eine Tabelle mit allen Formeln für alle Möglichkeiten, wie ihnen Dinge in Rechnung gestellt werden können. (…) Die zweite Datei ist die Liste der Dinge, für die ihnen im letzten Jahr Gebühren in Rechnung gestellt wurden. Es könnte heißen, ihnen wurden im letzten Jahr 1.800 Dollar für diese Kreditkarte berechnet, davon 1.200 Dollar für Zinszahlungen, für Verzugsgebühren, oder Währungstransfers und so weiter. Wir glauben nicht, dass sich irgendjemand diese Dateien jemals ansehen würde. Wir glauben, dass sofort Websites auftauchen würden, die diese Informationen verarbeiten würden. Diese Websites würden den folgenden Zwecken dienen. Erstens: Übersetzung. Sie würden dem Benutzer in einfachem Englisch erklären, was mit ihm passiert. Zweitens: Verhaltensänderung. Sie würden ihm erklären, dass er 1.800 Dollar bezahlt hat, weil er unfähig war, seine Rechnungen pünktlich zu bezahlen. Wenn er also eine automatische Zahlung einrichten würde, würde er viel Geld sparen. Drittens: Preisvergleich. Beachten sie bitte, dass die entsprechenden Unternehmen mit diesen Informationen die Nutzungsmuster kennen; und sie kennen alle Formeln für alle Kreditkartenunternehmen. Sie können also drei Kreditkartenunternehmen suchen, und finden, die für die Art und Weise, wie der Nutzer seine Kreditkarten verwendet, besser wären. Das ist das Konzept. (…)«
Jeff Bezos warf kurz darauf ein: »Außerdem werden sie bezahlt. Sie sind wie der Fuchs, der den Hühnerstall bewacht.«
Dem wachsamen Leser dürfte klar sein, dass wir heute genau von solchen System umgeben, überwacht, analysiert und bedrängt werden. Zu unserem Vorteil – wie Thaler meint.
Bemerkenswert in Bezug auf das, was uns noch bevorstehen könnte, ist die dritte Session der Master Class 2008. Thema: »Die Psychologie der Knappheit«. Teilnehmer – unter anderem: Jeff Bezos, Sean Parker, Elon Musk, Nathan Myhrvold, der 14 Jahre als Stratege für Bill Gates arbeitete, Daniel Hillis, ehemals Vizepräsident für Forschung und Entwicklung bei Disney und Vater des Parallel Computing, das die Grundlage für moderne Supercomputer darstellt, et cetera. Neben Richard Thaler sprach bei der dritten Session auch Sendhil Mullainathan, Volkswirt an der Harvard-Universität. Sein Spezialgebiet: Verhaltensökonomie und Armutsökonomik. Einleitend erklärte Mullainathan:
»Lassen wir die Armutsbekämpfung für einen Moment beiseite und fragen uns: Gibt es etwas, das der Armut innewohnt und das an und für sich eine Untersuchung wert ist? Einer der Gründe dafür ist, dass wir – abgesehen von Wundermitteln – verstehen müssen, ob es unter Bedingungen der Knappheit gemeinsame Prinzipien gibt, die uns helfen können, Verhalten zu verstehen und Interventionen zu gestalten. Wenn wir das Gefühl haben, dass Bedingungen der Knappheit bestimmte psychologische Effekte hervorrufen, dann wird das, ganz zu schweigen vom rein wissenschaftlichen Interesse, eine große Mehrheit der Interventionen beeinflussen. Das ist eine wichtige und alte Frage.«
Korrekt. Denn Schuldknechtschaft war, wie die künstliche Verknappung von Nahrungsmitteln, seit jeher ein beliebtes Mittel der herrschenden Kaste, um den Pöbel im Zaum, beziehungsweise mit existenziellen Problemen auf Trab zu halten. So hat er nämlich weder Zeit noch Energie, um mit Mistgabeln und Fackeln gen Elfenbeinturm aufzubrechen. In diesem Zusammenhang sei nochmals auf »Food Chain Reaction – A Global Food Security Game« hingewiesen, ein Planspiel, das im November 2015 vom tiefenstaatlichen Center for American Progress, dem World Wildlife Fund, Center for Naval Analyses (CNA), Cargill und Mars durchgeführt wurde und Nahrungsmittelknappheit im Zeitraum von 2020 bis 2030 simulierte.
Der Einblick in die Ausbildungsprozesse der Edge-Foundation und die Liste ihrer Teilnehmer gibt somit allen Anlass zu befürchten, dass Brockmans »Internetsalon« die zentralen Akteure der kontinuierlich engmaschiger greifenden Technokratie nicht nur in puncto Social Engineering ausbilden, sondern sie darüber hinaus auf eine Zeit von Mangelwirtschaft und massiver Armut vorbereiten wollte. Auf die »Dritte Kultur«. Die wohlstandsvernichtende Tokenisierung der Welt.
Dabei sollte nicht vergessen werden, dass Brockman vermutlich nur ein geschäftstüchtiger Narzisst mit sozialen Kompetenzen war, der seine Chance auf Geld und Rampenlicht geschickt zu nutzen wusste – und dass Jeffrey Epstein als maßgeblicher Finanzier der Edge-Foundation nicht einfach im Alleingang handelte. Denn Epstein war Doppelagent, unterwegs im Auftrag von CIA und Mossad. Mindestens. Dass er mittlerweile nicht mehr unter den Lebenden weilt, dürfte weder sein Geheimdienstnetzwerk noch seinen elitären Kundenstamm davon abgehalten haben, sein schmutziges Geschäft weiterzubetreiben.
Man kann also durchaus mit einem metaphorisch zu lesenden Zitat aus jenem kultigen 60er-Film schließen, dessen Titel nun als Bezeichnung für ein Septett börsennotierter Technokratie-Operatoren missbraucht wird:
»Das Blutvergießen wird so lange weitergehen, bis die Ursache dafür ausgehoben ist.«
-
 @ be7bf5de:09420d0a
2025-01-02 17:54:35
@ be7bf5de:09420d0a
2025-01-02 17:54:35The SALUD Decentralized Health App Development Challenge is an exciting initiative aimed at revolutionizing healthcare through the use of decentralized technologies. Running from January to May, this challenge will bring together developers, designers, healthcare providers, and health conscious individuals interested in decentralizing healthcare. Participants will create open-source tools leveraging Nostr, Bitcoin, and the SALUD protocol aiming to improve healthcare access, enhance data portability, and ultimately improve health outcomes for individuals worldwide.
Challenge Mission
At its core, the mission of this challenge is to bootstrap an ecosystem of interoperable tools that allow individuals to take full control of their health data. By building apps on the Nostr protocol and integrating bitcoin, the challenge hopes to address key issues in traditional healthcare, including access to services, privacy, and fragmented health data systems. All participating apps will be required to be compatible with the SALUD protocol, or Sistema de Administración de Libertad Único y Decentralizado, which is an open-source framework for utilizing health data over Nostr.
Challenge Structure
The challenge is structured to span five months, from January through May. Throughout this period, participants will meet weekly to discuss their progress, share insights, and collaborate with others. These sessions will be instrumental in connecting developers, designers, and healthcare professionals, fostering a community focused on building the future of decentralized healthcare.
The challenge will include weekly office hours for participants, held every Thursday at 11 AM Eastern Time (4 PM UTC), starting on January 16th. These open office hours will provide opportunities to connect with doctors, developers, entrepreneurs, and health-minded bitcoiners to ensure that the apps being developed address real-world healthcare needs.
Evaluation Criteria
All submissions to the challenge will be evaluated based on four key metrics:
- App Production Readiness: Is the app functional and polished enough for real-world use?
- Solution Depth and Creativity: How innovative and impactful is the solution in addressing healthcare challenges?
- Interoperability: How well does the app integrate with the SALUD protocol and other healthcare tools, ensuring it can work seamlessly within the decentralized ecosystem?
- Overall Contribution to the Ecosystem: Does the app contribute to the broader vision of decentralized healthcare and enhance individual control over health data?
Prize Pool
The challenge features a prize pool starting at 10 million satoshis (0.1 BTC). Winning participants will not only receive financial rewards but also have the opportunity to collaborate with NosFabrica, a leading force in decentralized technology development, and Illuminodes, piloting the SALUD protocol in El Salvador. This container provides an exciting pathway for long-term collaboration and innovation in the global and decentralized health space.
Who Should Participate?
This challenge is open to a wide range of participants, each contributing unique expertise and perspectives:
- Developers and Designers: Those skilled in app development, UX/UI design, bitcoin and the Lightning Network.
- Healthcare Providers (Doctors/Nurses/Alternative Health): Professionals who can offer insights into real-world healthcare needs and help design solutions that truly benefit patients.
- Health-Conscious Individuals: People passionate about taking control of their own health data and empowering others to do the same.
- Bitcoiners and Nostriches: Enthusiasts of Bitcoin and Nostr who are excited to apply these censorship resistant technologies to solve pressing issues in healthcare.
- Investors: Individuals or firms interested in supporting innovative projects and startups that have the potential to shape future of healthcare.
How to Participate
To get involved in the challenge and receive important updates and event invitations, participants can sign up through either of the provided forms:
The main categories we'll encourage individuals to develop solutions for are personal health apps, healthcare provider tooling, and SALUD protocol infrastructure. So far, the SALUD protocol includes NIP-82, a way to store FHIR healthcare records on Nostr, developed by NosFabrica co-founder, Vitor Pamplona. We see more Nostr improvement proposals being made as healthcare data use cases develop.
Conclusion
The SALUD Decentralized Health App Development Challenge is a groundbreaking opportunity for anyone passionate about using Nostr and Bitcoin to reshape the healthcare landscape. By building apps that empower individuals to control their own health data, participants will play a pivotal role in addressing some of the most pressing challenges in modern healthcare, from data privacy to accessibility and portability. We're xcited about this challenge and to continue building the future of decentralized healthcare!
Happy new year!
PS. Feel free to reach out with any questions to jon@nosfabrica.com or go to https://nosfabrica.com/challenge/ to learn more.
-
 @ ac8bb9b0:70278acc
2024-12-20 18:48:36
@ ac8bb9b0:70278acc
2024-12-20 18:48:36Details
- ⏲️ Prep time: 5
- 🍳 Cook time: 10
- 🍽️ Servings: 4
Ingredients
- 1 lb large shrimp, peeled and deveined
- 1 tablespoon extra virgin olive oil
- 3 cloves garlic, chopped
- 1/4 cup white wine, dry
- 14 oz can petite diced tomatoes, drained
- 1/2 cup half and half
- 1/2 teaspoon dried oregano
- kosher salt and fresh black pepper, to taste
- 1 teaspoon lemon juice
- 1/4 cup fresh parsley, chopped
- 8 ounces angel hair pasta, whole wheat, gluten-free or high fiber
Directions
- Boil water with salt in a large pot for the pasta. Cook pasta al dente according to package directions.
- Meanwhile, season shrimp with 1/4 teaspoon salt, black pepper and oregano.
- Heat a large skillet over medium heat. Add the oil, when warm add the shrimp and garlic and cook about 2 minutes on each side.
- Add tomatoes, wine, salt and pepper and cook an additional minute.
- Remove from heat and stir in half and half. Add lemon juice and parsley and serve over pasta.
- Divide equally in 4 plates or shallow bowls.
-
 @ ccc8ee23:9f3d9783
2024-12-19 12:46:00
@ ccc8ee23:9f3d9783
2024-12-19 12:46:00Chef's notes
Salmon Mentai Rice. Create your own layers of fluffy, seasoned rice are topped with tender, pan-seared chicken or salmon and a creamy, spicy mentai sauce made with spicy Japanese mayo .
Torched to golden perfection, it’s finished with nori and tobiko for a burst of texture and flavor. A simple tasty Japanese fusion delight that’s perfect🤩
Subtitude of Tobiko, white sesame seeds as economical option will add a nutty flavor and subtle crunch to the dish for texture and visual appeal.
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 30 min
- 🍽️ Servings: 2
Ingredients
- Steamed Rice 400 grams
- Rice vinegar 1 tbsp
- Sugar 1 tsp
- chicken breast / thighs 250 grams
- soy sauce 1 tbsp
- oyster sauce 1 tbsp
- sesame oil 1 tsp
- garlic powder 1 tsp
- cooking oil 1 tbsp
- mayonnaise (e.g., Kewpie) 4 tbsp
- sriracha or any chili sauce 1 tbsp
- tobiko if any or white sesame as optional, for texture, 2 tsp only
Directions
- Prepared the Rice: mixed in bowl 2 cups steam rice, 1 tbsp rice vinegar, 1 tsp sugar and 1/2 tsp salt. Set a side.
- Cook the Chicken: 1. Marinate the chicken pieces with 1 tsp soy sauce, 1 tsp oyster sauce, 1 tsp sesame oil, 1 tsp garlic powder for 15–20 minutes. 2. Heat cooking oil in a pan over medium heat and stir-fry the chicken until fully cooked and slightly caramelized. Remove from heat.
- Make the Mentai Sauce 1. In a small bowl, combine 4 tbsp mayonnaise, 1 tbsp chili sauce, and 1 tsp sesame oil. Add tobiko if desired for texture. Mix well.
- Assemble the Mentai Rice 1. In a heatproof bowl or tray, layer the seasoned rice as the base. 2. Add a layer of cooked chicken on top of the rice. 3. Spread the mentai sauce evenly over the chicken layer.
- Grill or Broil: Use a kitchen torch or place the dish under a broiler for 2–3 minutes until the sauce is slightly charred and bubbly.
- Garnish with white sesame or nori strips, or extra tobiko.
-
 @ 3f770d65:7a745b24
2024-12-31 17:03:46
@ 3f770d65:7a745b24
2024-12-31 17:03:46Here are my predictions for Nostr in 2025:
Decentralization: The outbox and inbox communication models, sometimes referred to as the Gossip model, will become the standard across the ecosystem. By the end of 2025, all major clients will support these models, providing seamless communication and enhanced decentralization. Clients that do not adopt outbox/inbox by then will be regarded as outdated or legacy systems.
Privacy Standards: Major clients such as Damus and Primal will move away from NIP-04 DMs, adopting more secure protocol possibilities like NIP-17 or NIP-104. These upgrades will ensure enhanced encryption and metadata protection. Additionally, NIP-104 MLS tools will drive the development of new clients and features, providing users with unprecedented control over the privacy of their communications.
Interoperability: Nostr's ecosystem will become even more interconnected. Platforms like the Olas image-sharing service will expand into prominent clients such as Primal, Damus, Coracle, and Snort, alongside existing integrations with Amethyst, Nostur, and Nostrudel. Similarly, audio and video tools like Nostr Nests and Zap.stream will gain seamless integration into major clients, enabling easy participation in live events across the ecosystem.
Adoption and Migration: Inspired by early pioneers like Fountain and Orange Pill App, more platforms will adopt Nostr for authentication, login, and social systems. In 2025, a significant migration from a high-profile application platform with hundreds of thousands of users will transpire, doubling Nostr’s daily activity and establishing it as a cornerstone of decentralized technologies.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A Causa
o Princípios de Economia Política de Menger é o único livro que enfatiza a CAUSA o tempo todo. os cientistas todos parecem não saber, ou se esquecer sempre, que as coisas têm causa, e que o conhecimento verdadeiro é o conhecimento da causa das coisas.
a causa é uma categoria metafísica muito superior a qualquer correlação ou resultado de teste de hipótese, ela não pode ser descoberta por nenhum artifício econométrico ou reduzida à simples antecedência temporal estatística. a causa dos fenômenos não pode ser provada cientificamente, mas pode ser conhecida.
o livro de Menger conta para o leitor as causas de vários fenômenos econômicos e as interliga de forma que o mundo caótico da economia parece adquirir uma ordem no momento em que você lê. é uma sensação mágica e indescritível.
quando eu te o recomendei, queria é te imbuir com o espírito da busca pela causa das coisas. depois de ler aquilo, você está apto a perceber continuidade causal nos fenômenos mais complexos da economia atual, enxergar as causas entre toda a ação governamental e as suas várias consequências na vida humana. eu faço isso todos os dias e é a melhor sensação do mundo quando o caos das notícias do caderno de Economia do jornal -- que para o próprio jornalista que as escreveu não têm nenhum sentido (tanto é que ele escreve tudo errado) -- se incluem num sistema ordenado de causas e consequências.
provavelmente eu sempre erro em alguns ou vários pontos, mas ainda assim é maravilhoso. ou então é mais maravilhoso ainda quando eu descubro o erro e reinsiro o acerto naquela racionalização bela da ordem do mundo econômico que é a ordem de Deus.
em scrap para T.P.
-
 @ 0a9436f8:9935ad4f
2024-12-12 00:10:17
@ 0a9436f8:9935ad4f
2024-12-12 00:10:17Introduction
1. The Industrial Revolution and its consequences have been a disaster for the human race. They have greatly increased the life-expectancy of those of us who live in "advanced" countries, but they have destabilized society, have made life unfulfilling, have subjected human beings to indignities, have led to widespread psychological suffering (in the Third World to physical suffering as well) and have inflicted severe damage on the natural world. The continued development of technology will worsen the situation. It will certainly subject human beings to greater indignities and inflict greater damage on the natural world, it will probably lead to greater social disruption and psychological suffering, and it may lead to increased physical suffering even in "advanced" countries.
2. The industrial-technological system may survive or it may break down. If it survives, it MAY eventually achieve a low level of physical and psychological suffering, but only after passing through a long and very painful period of adjustment and only at the cost of permanently reducing human beings and many other living organisms to engineered products and mere cogs in the social machine. Furthermore, if the system survives, the consequences will be inevitable: There is no way of reforming or modifying the system so as to prevent it from depriving people of dignity and autonomy.
3. If the system breaks down the consequences will still be very painful. But the bigger the system grows the more disastrous the results of its breakdown will be, so if it is to break down it had best break down sooner rather than later.
4. We therefore advocate a revolution against the industrial system. This revolution may or may not make use of violence; it may be sudden or it may be a relatively gradual process spanning a few decades. We can't predict any of that. But we do outline in a very general way the measures that those who hate the industrial system should take in order to prepare the way for a revolution against that form of society. This is not to be a POLITICAL revolution. Its object will be to overthrow not governments but the economic and technological basis of the present society.
5. In this article we give attention to only some of the negative developments that have grown out of the industrial-technological system. Other such developments we mention only briefly or ignore altogether. This does not mean that we regard these other developments as unimportant. For practical reasons we have to confine our discussion to areas that have received insufficient public attention or in which we have something new to say. For example, since there are well-developed environmental and wilderness movements, we have written very little about environmental degradation or the destruction of wild nature, even though we consider these to be highly important.
THE PSYCHOLOGY OF MODERN LEFTISM
6. Almost everyone will agree that we live in a deeply troubled society. One of the most widespread manifestations of the craziness of our world is leftism, so a discussion of the psychology of leftism can serve as an introduction to the discussion of the problems of modern society in general.
7. But what is leftism? During the first half of the 20th century leftism could have been practically identified with socialism. Today the movement is fragmented and it is not clear who can properly be called a leftist. When we speak of leftists in this article we have in mind mainly socialists, collectivists, "politically correct" types, feminists, gay and disability activists, animal rights activists and the like. But not everyone who is associated with one of these movements is a leftist. What we are trying to get at in discussing leftism is not so much movement or an ideology as a psychological type, or rather a collection of related types. Thus, what we mean by "leftism" will emerge more clearly in the course of our discussion of leftist psychology. (Also, see paragraphs 227-230.)
8. Even so, our conception of leftism will remain a good deal less clear than we would wish, but there doesn't seem to be any remedy for this. All we are trying to do here is indicate in a rough and approximate way the two psychological tendencies that we believe are the main driving force of modern leftism. We by no means claim to be telling the WHOLE truth about leftist psychology. Also, our discussion is meant to apply to modern leftism only. We leave open the question of the extent to which our discussion could be applied to the leftists of the 19th and early 20th centuries.
9. The two psychological tendencies that underlie modern leftism we call "feelings of inferiority" and "oversocialization." Feelings of inferiority are characteristic of modern leftism as a whole, while oversocialization is characteristic only of a certain segment of modern leftism; but this segment is highly influential.
FEELINGS OF INFERIORITY
10. By "feelings of inferiority" we mean not only inferiority feelings in the strict sense but a whole spectrum of related traits; low self-esteem, feelings of powerlessness, depressive tendencies, defeatism, guilt, self-hatred, etc. We argue that modern leftists tend to have some such feelings (possibly more or less repressed) and that these feelings are decisive in determining the direction of modern leftism.
11. When someone interprets as derogatory almost anything that is said about him (or about groups with whom he identifies) we conclude that he has inferiority feelings or low self-esteem. This tendency is pronounced among minority rights activists, whether or not they belong to the minority groups whose rights they defend. They are hypersensitive about the words used to designate minorities and about anything that is said concerning minorities. The terms "negro," "oriental," "handicapped" or "chick" for an African, an Asian, a disabled person or a woman originally had no derogatory connotation. "Broad" and "chick" were merely the feminine equivalents of "guy," "dude" or "fellow." The negative connotations have been attached to these terms by the activists themselves. Some animal rights activists have gone so far as to reject the word "pet" and insist on its replacement by "animal companion." Leftish anthropologists go to great lengths to avoid saying anything about primitive peoples that could conceivably be interpreted as negative. They want to replace the world "primitive" by "nonliterate." They seem almost paranoid about anything that might suggest that any primitive culture is inferior to our own. (We do not mean to imply that primitive cultures ARE inferior to ours. We merely point out the hypersensitivity of leftish anthropologists.)
12. Those who are most sensitive about "politically incorrect" terminology are not the average black ghetto-dweller, Asian immigrant, abused woman or disabled person, but a minority of activists, many of whom do not even belong to any "oppressed" group but come from privileged strata of society. Political correctness has its stronghold among university professors, who have secure employment with comfortable salaries, and the majority of whom are heterosexual white males from middle- to upper-middle-class families.
13. Many leftists have an intense identification with the problems of groups that have an image of being weak (women), defeated (American Indians), repellent (homosexuals) or otherwise inferior. The leftists themselves feel that these groups are inferior. They would never admit to themselves that they have such feelings, but it is precisely because they do see these groups as inferior that they identify with their problems. (We do not mean to suggest that women, Indians, etc. ARE inferior; we are only making a point about leftist psychology.)
14. Feminists are desperately anxious to prove that women are as strong and as capable as men. Clearly they are nagged by a fear that women may NOT be as strong and as capable as men.
15. Leftists tend to hate anything that has an image of being strong, good and successful. They hate America, they hate Western civilization, they hate white males, they hate rationality. The reasons that leftists give for hating the West, etc. clearly do not correspond with their real motives. They SAY they hate the West because it is warlike, imperialistic, sexist, ethnocentric and so forth, but where these same faults appear in socialist countries or in primitive cultures, the leftist finds excuses for them, or at best he GRUDGINGLY admits that they exist; whereas he ENTHUSIASTICALLY points out (and often greatly exaggerates) these faults where they appear in Western civilization. Thus it is clear that these faults are not the leftist's real motive for hating America and the West. He hates America and the West because they are strong and successful.
16. Words like "self-confidence," "self-reliance," "initiative," "enterprise," "optimism," etc., play little role in the liberal and leftist vocabulary. The leftist is anti-individualistic, pro-collectivist. He wants society to solve everyone's problems for them, satisfy everyone's needs for them, take care of them. He is not the sort of person who has an inner sense of confidence in his ability to solve his own problems and satisfy his own needs. The leftist is antagonistic to the concept of competition because, deep inside, he feels like a loser.
17. Art forms that appeal to modern leftish intellectuals tend to focus on sordidness, defeat and despair, or else they take an orgiastic tone, throwing off rational control as if there were no hope of accomplishing anything through rational calculation and all that was left was to immerse oneself in the sensations of the moment.
18. Modern leftish philosophers tend to dismiss reason, science, objective reality and to insist that everything is culturally relative. It is true that one can ask serious questions about the foundations of scientific knowledge and about how, if at all, the concept of objective reality can be defined. But it is obvious that modern leftish philosophers are not simply cool-headed logicians systematically analyzing the foundations of knowledge. They are deeply involved emotionally in their attack on truth and reality. They attack these concepts because of their own psychological needs. For one thing, their attack is an outlet for hostility, and, to the extent that it is successful, it satisfies the drive for power. More importantly, the leftist hates science and rationality because they classify certain beliefs as true (i.e., successful, superior) and other beliefs as false (i.e., failed, inferior). The leftist's feelings of inferiority run so deep that he cannot tolerate any classification of some things as successful or superior and other things as failed or inferior. This also underlies the rejection by many leftists of the concept of mental illness and of the utility of IQ tests. Leftists are antagonistic to genetic explanations of human abilities or behavior because such explanations tend to make some persons appear superior or inferior to others. Leftists prefer to give society the credit or blame for an individual's ability or lack of it. Thus if a person is "inferior" it is not his fault, but society's, because he has not been brought up properly.
19. The leftist is not typically the kind of person whose feelings of inferiority make him a braggart, an egotist, a bully, a self-promoter, a ruthless competitor. This kind of person has not wholly lost faith in himself. He has a deficit in his sense of power and self-worth, but he can still conceive of himself as having the capacity to be strong, and his efforts to make himself strong produce his unpleasant behavior. [1] But the leftist is too far gone for that. Hisfeelings of inferiority are so ingrained that he cannot conceive of himself as individually strong and valuable. Hence the collectivism of the leftist. He can feel strong only as a member of a large organization or a mass movement with which he identifies himself.
20. Notice the masochistic tendency of leftist tactics. Leftists protest by lying down in front of vehicles, they intentionally provoke police or racists to abuse them, etc. These tactics may often be effective, but many leftists use them not as a means to an end but because they PREFER masochistic tactics. Self-hatred is a leftist trait.
21. Leftists may claim that their activism is motivated by compassion or by moral principles, and moral principle does play a role for the leftist of the oversocialized type. But compassion and moral principle cannot be the main motives for leftist activism. Hostility is too prominent a component of leftist behavior; so is the drive for power. Moreover, much leftist behavior is not rationally calculated to be of benefit to the people whom the leftists claim to be trying to help. For example, if one believes that affirmative action is good for black people, does it make sense to demand affirmative action in hostile or dogmatic terms? Obviously it would be more productive to take a diplomatic and conciliatory approach that would make at least verbal and symbolic concessions to white people who think that affirmative action discriminates against them. But leftist activists do not take such an approach because it would not satisfy their emotional needs. Helping black people is not their real goal. Instead, race problems serve as an excuse for them to express their own hostility and frustrated need for power. In doing so they actually harm black people, because the activists' hostile attitude toward the white majority tends to intensify race hatred.
22. If our society had no social problems at all, the leftists would have to INVENT problems in order to provide themselves with an excuse for making a fuss.
23. We emphasize that the foregoing does not pretend to be an accurate description of everyone who might be considered a leftist. It is only a rough indication of a general tendency of leftism.
OVERSOCIALIZATION
24. Psychologists use the term "socialization" to designate the process by which children are trained to think and act as society demands. A person is said to be well socialized if he believes in and obeys the moral code of his society and fits in well as a functioning part of that society. It may seem senseless to say that many leftists are oversocialized, since the leftist is perceived as a rebel. Nevertheless, the position can be defended. Many leftists are not such rebels as they seem.
25. The moral code of our society is so demanding that no one can think, feel and act in a completely moral way. For example, we are not supposed to hate anyone, yet almost everyone hates somebody at some time or other, whether he admits it to himself or not. Some people are so highly socialized that the attempt to think, feel and act morally imposes a severe burden on them. In order to avoid feelings of guilt, they continually have to deceive themselves about their own motives and find moral explanations for feelings and actions that in reality have a non-moral origin. We use the term "oversocialized" to describe such people. [2]
26. Oversocialization can lead to low self-esteem, a sense of powerlessness, defeatism, guilt, etc. One of the most important means by which our society socializes children is by making them feel ashamed of behavior or speech that is contrary to society's expectations. If this is overdone, or if a particular child is especially susceptible to such feelings, he ends by feeling ashamed of HIMSELF. Moreover the thought and the behavior of the oversocialized person are more restricted by society's expectations than are those of the lightly socialized person. The majority of people engage in a significant amount of naughty behavior. They lie, they commit petty thefts, they break traffic laws, they goofoff at work, they hate someone, they say spiteful things or they use some underhanded trick to get ahead of the other guy. The oversocialized person cannot do these things, or if he does do them he generates in himself a sense of shame and self-hatred. The oversocialized person cannot even experience, without guilt, thoughts or feelings that are contrary to the accepted morality; he cannot think "unclean" thoughts. And socialization is not just a matter of morality; we are socialized to conform to many norms of behavior that do not fall under the heading of morality. Thus the oversocialized person is kept on a psychological leash and spends his life running on rails that society has laid down for him. In many oversocialized people this results in a sense of constraint and powerlessness that can be a severe hardship. We suggest that oversocialization is among the more serious cruelties that human beings inflict on one another.
27. We argue that a very important and influential segment of the modern left is oversocialized and that their oversocialization is of great importance in determining the direction of modern leftism. Leftists of the oversocialized type tend to be intellectuals or members of the upper-middle class. Notice that university intellectuals [3] constitute the most highly socialized segment of our society and also the most left-wing segment.
28. The leftist of the oversocialized type tries to get off his psychological leash and assert his autonomy by rebelling. But usually he is not strong enough to rebel against the most basic values of society. Generally speaking, the goals of today's leftists are NOT in conflict with the accepted morality. On the contrary, the left takes an accepted moral principle, adopts it as its own, and then accuses mainstream society of violating that principle. Examples: racial equality, equality of the sexes, helping poor people, peace as opposed to war, nonviolence generally, freedom of expression, kindness to animals. More fundamentally, the duty of the individual to serve society and the duty of society to take care of the individual. All these have been deeply rooted values of our society (or at least of its middle and upper classes [4] for a long time. These values are explicitly or implicitly expressed or presupposed in most of the material presented to us by the mainstream communications media and the educational system. Leftists, especially those of the oversocialized type, usually do not rebel against these principles but justify their hostility to society by claiming (with some degree of truth) that society is not living up to these principles.
29. Here is an illustration of the way in which the oversocialized leftist shows his real attachment to the conventional attitudes of our society while pretending to be in rebellion against it. Many leftists push for affirmative action, for moving black people into high-prestige jobs, for improved education in black schools and more money for such schools; the way of life of the black "underclass" they regard as a social disgrace. They want to integrate the black man into the system, make him a business executive, a lawyer, a scientist just like upper-middle-class white people. The leftists will reply that the last thing they want is to make the black man into a copy of the white man; instead, they want to preserve African American culture. But in what does this preservation of African American culture consist? It can hardly consist in anything more than eating black-style food, listening to black-style music, wearing black-style clothing and going to a black-style church or mosque. In other words, it can express itself only in superficial matters. In all ESSENTIAL respects most leftists of the oversocialized type want to make the black man conform to white, middle-class ideals. They want to make him study technical subjects, become an executive or a scientist, spend his life climbing the status ladder to prove that black people are as good as white. They want to make black fathers "responsible," they want black gangs to become nonviolent, etc. But these are exactly the values of the industrial-technological system. The system couldn't care less what kind of music a man listens to, what kind of clothes he wears or what religion he believes in as long as he studies in school, holds a respectable job, climbs the status ladder, is a "responsible" parent, is nonviolent and so forth. In effect, however much he may deny it, the oversocialized leftist wants to integrate the black man into the system and make him adopt its values.
30. We certainly do not claim that leftists, even of the oversocialized type, NEVER rebel against the fundamental values of our society. Clearly they sometimes do. Some oversocialized leftists have gone so far as to rebel against one of modern society's most important principles by engaging in physical violence. By their own account, violence is for them a form of "liberation." In other words, by committing violence they break through the psychological restraints that have been trained into them. Because they are oversocialized these restraints have been more confining for them than for others; hence their need to break free of them. But they usually justify their rebellion in terms of mainstream values. If they engage in violence they claim to be fighting against racism or the like.
31. We realize that many objections could be raised to the foregoing thumbnail sketch of leftist psychology. The real situation is complex, and anything like a complete description of it would take several volumes even if the necessary data were available. We claim only to have indicated very roughly the two most important tendencies in the psychology of modern leftism.
32. The problems of the leftist are indicative of the problems of our society as a whole. Low self-esteem, depressive tendencies and defeatism are not restricted to the left. Though they are especially noticeable in the left, they are widespread in our society. And today's society tries to socialize us to a greater extent than any previous society. We are even told by experts how to eat, how to exercise, how to make love, how to raise our kids and so forth.
THE POWER PROCESS
33. Human beings have a need (probably based in biology) for something that we will call the "power process." This is closely related to the need for power (which is widely recognized) but is not quite the same thing. The power process has four elements. The three most clear-cut of these we call goal, effort and attainment of goal. (Everyone needs to have goals whose attainment requires effort, and needs to succeed in attaining at least some of his goals.) The fourth element is more difficult to define and may not be necessary for everyone. We call it autonomy and will discuss it later (paragraphs 42-44).
34. Consider the hypothetical case of a man who can have anything he wants just by wishing for it. Such a man has power, but he will develop serious psychological problems. At first he will have a lot of fun, but by and by he will become acutely bored and demoralized. Eventually he may become clinically depressed. History shows that leisured aristocracies tend to become decadent. This is not true of fighting aristocracies that have to struggle to maintain their power. But leisured, secure aristocracies that have no need to exert themselves usually become bored, hedonistic and demoralized, even though they have power. This shows that power is not enough. One must have goals toward which to exercise one's power.
35. Everyone has goals; if nothing else, to obtain the physical necessities of life: food, water and whatever clothing and shelter are made necessary by the climate. But the leisured aristocrat obtains these things without effort. Hence his boredom and demoralization.
36. Nonattainment of important goals results in death if the goals are physical necessities, and in frustration if nonattainment of the goals is compatible with survival. Consistent failure to attain goals throughout life results in defeatism, low self-esteem or depression.
37, Thus, in order to avoid serious psychological problems, a human being needs goals whose attainment requires effort, and he must have a reasonable rate of success in attaining his goals.
SURROGATE ACTIVITIES
38. But not every leisured aristocrat becomes bored and demoralized. For example, the emperor Hirohito, instead of sinking into decadent hedonism, devoted himself to marine biology, a field in which he became distinguished. When people do not have to exert themselves to satisfy their physical needs they often set up artificial goals for themselves. In many cases they then pursue these goals with the same energy and emotional involvement that they otherwise would have put into the search for physical necessities. Thus the aristocrats of the Roman Empire had their literary pretensions; many European aristocrats a few centuries ago invested tremendous time and energy in hunting, though they certainly didn't need the meat; other aristocracies have competed for status through elaborate displays of wealth; and a few aristocrats, like Hirohito, have turned to science.
39. We use the term "surrogate activity" to designate an activity that is directed toward an artificial goal that people set up for themselves merely in order to have some goal to work toward, or let us say, merely for the sake of the "fulfillment" that they get from pursuing the goal. Here is a rule of thumb for the identification of surrogate activities. Given a person who devotes much time and energy to the pursuit of goal X, ask yourself this: If he had to devote most of his time and energy to satisfying his biological needs, and if that effort required him to use his physical and mental faculties in a varied and interesting way, would he feel seriously deprived because he did not attain goal X? If the answer is no, then the person's pursuit of goal X is a surrogate activity. Hirohito's studies in marine biology clearly constituted a surrogate activity, since it is pretty certain that if Hirohito had had to spend his time working at interesting non-scientific tasks in order to obtain the necessities of life, he would not have felt deprived because he didn't know all about the anatomy and life-cycles of marine animals. On the other hand the pursuit of sex and love (for example) is not a surrogate activity, because most people, even if their existence were otherwise satisfactory, would feel deprived if they passed their lives without ever having a relationship with a member of the opposite sex. (But pursuit of an excessive amount of sex, more than one really needs, can be a surrogate activity.)
40. In modern industrial society only minimal effort is necessary to satisfy one's physical needs. It is enough to go through a training program to acquire some petty technical skill, then come to work on time and exert the very modest effort needed to hold a job. The only requirements are a moderate amount of intelligence and, most of all, simple OBEDIENCE. If one has those, society takes care of one from cradle to grave. (Yes, there is an underclass that cannot take the physical necessities for granted, but we are speaking here of mainstream society.) Thus it is not surprising that modern society is full of surrogate activities. These include scientific work, athletic achievement, humanitarian work, artistic and literary creation, climbing the corporate ladder, acquisition of money and material goods far beyond the point at which they cease to give any additional physical satisfaction, and social activism when it addresses issues that are not important for the activist personally, as in the case of white activists who work for the rights of nonwhite minorities. These are not always PURE surrogate activities, since for many people they may be motivated in part by needs other than the need to have some goal to pursue. Scientific work may be motivated in part by a drive for prestige, artistic creation by a need to express feelings, militant social activism by hostility. But for most people who pursue them, these activities are in large part surrogate activities. For example, the majority of scientists will probably agree that the "fulfillment" they get from their work is more important than the money and prestige they earn.
41. For many if not most people, surrogate activities are less satisfying than the pursuit of real goals (that is, goals that people would want to attain even if their need for the power process were already fulfilled). One indication of this is the fact that, in many or most cases, people who are deeply involved in surrogate activities are never satisfied, never at rest. Thus the money-maker constantly strives for more and more wealth. The scientist no sooner solves one problem than he moves on to the next. The long-distance runner drives himself to run always farther and faster. Many people who pursue surrogate activities will say that they get far more fulfillment from these activities than they do from the "mundane" business of satisfying their biological needs, but that is because in our society the effort needed to satisfy the biological needs has been reduced to triviality. More importantly, in our society people do not satisfy their biological needs AUTONOMOUSLY but by functioning as parts of an immense social machine. In contrast, people generally have a great deal of autonomy in pursuing their surrogate activities.
AUTONOMY
42. Autonomy as a part of the power process may not be necessary for every individual. But most people need a greater or lesser degree of autonomy in working toward their goals. Their efforts must be undertaken on their own initiative and must be under their own direction and control. Yet most people do not have to exert this initiative, direction and control as single individuals. It is usually enough to act as a member of a SMALL group. Thus if half a dozen people discuss a goal among themselves and make a successful joint effort to attain that goal, their need for the power process will be served. But if they work under rigid orders handed down from above that leave them no room for autonomous decision and initiative, then their need for the power process will not be served. The same is true when decisions are made on a collective basis if the group making the collective decision is so large that the role of each individual is insignificant. [5]
43. It is true that some individuals seem to have little need for autonomy. Either their drive for power is weak or they satisfy it by identifying themselves with some powerful organization to which they belong. And then there are unthinking, animal types who seem to be satisfied with a purely physical sense of power (the good combat soldier, who gets his sense of power by developing fighting skills that he is quite content to use in blind obedience to his superiors).
44. But for most people it is through the power processshaving a goal, making an AUTONOMOUS effort and attaining the goalsthat self-esteem, self-confidence and a sense of power are acquired. When one does not have adequate opportunity to go through the power process the consequences are (depending on the individual and on the way the power process is disrupted) boredom, demoralization, low self-esteem, inferiority feelings, defeatism, depression, anxiety, guilt, frustration, hostility, spouse or child abuse, insatiable hedonism, abnormal sexual behavior, sleep disorders, eating disorders, etc. [6]
SOURCES OF SOCIAL PROBLEMS
45. Any of the foregoing symptoms can occur in any society, but in modern industrial society they are present on a massive scale. We aren't the first to mention that the world today seems to be going crazy. This sort of thing is not normal for human societies. There is good reason to believe that primitive man suffered from less stress and frustration and was better satisfied with his way of life than modern man is. It is true that not all was sweetness and light in primitive societies. Abuse of women was common among the Australian aborigines, transexuality was fairly common among some of the American Indian tribes. But it does appear that GENERALLY SPEAKING the kinds of problems that we have listed in the preceding paragraph were far less common among primitive peoples than they are in modern society.
46. We attribute the social and psychological problems of modern society to the fact that that society requires people to live under conditions radically different from those under which the evolved and to behave in ways that conflict with the patterns of behavior that the human race developed while living under the earlier conditions. It is clear from what we have already written that we consider lack of opportunity to properly experience the power process as the most important of the abnormal conditions to which modern society subjects people. But it is not the only one. Before dealing with disruption of the power process as a source of social problems we will discuss some of the other sources.
47. Among the abnormal conditions present in modern industrial society are excessive density of population, isolation of man from nature, excessive rapidity of social change and the breakdown of natural small-scale communities such as the extended family, the village or the tribe.
48. It is well known that crowding increases stress and aggression. The degree of crowding that exists today and the isolation of man from nature are consequences of technological progress. All pre-industrial societies were predominantly rural. The Industrial Revolution vastly increased the size of cities and the proportion of the population that lives in them, and modern agricultural technology has made it possible for the Earth to support a far denser population than it ever did before. (Also, technology exacerbates the effects of crowding because it puts increased disruptive powers in people's hands. For example, a variety of noise-making devices: power mowers, radios, motorcycles, etc. If the use of these devices is unrestricted, people who want peace and quiet are frustrated by the noise. If their use is restricted, people who use the devices are frustrated by the regulations. But if these machines had never been invented there would have been no conflict and no frustration generated by them.)
49. For primitive societies the natural world (which usually changes only slowly) provided a stable framework and therefore a sense of security. In the modern world it is human society that dominates nature rather than the other way around, and modern society changes very rapidly owing to technological change. Thus there is no stable framework.
50. The conservatives are fools: They whine about the decay of traditional values, yet they enthusiastically support technological progress and economic growth. Apparently it never occurs to them that you can't make rapid, drastic changes in the technology and the economy of a society without causing rapid changes in all other aspects of the society as well, and that such rapid changes inevitably break down traditional values.
51. The breakdown of traditional values to some extent implies the breakdown of the bonds that hold together traditional small-scale social groups. The disintegration of small-scale social groups is also promoted by the fact that modern conditions often require or tempt individuals to move to new locations, separating themselves from their communities. Beyond that, a technological society HAS TO weaken family ties and local communities if it is to function efficiently. In modern society an individual's loyalty must be first to the system and only secondarily to a small-scale community, because if the internal loyalties of small-scale communities were stronger than loyalty to the system, such communities would pursue their own advantage at the expense of the system.
52. Suppose that a public official or a corporation executive appoints his cousin, his friend or his co-religionist to a position rather than appointing the person best qualified for the job. He has permitted personal loyalty to supersede his loyalty to the system, and that is "nepotism" or "discrimination," both of which are terrible sins in modern society. Would-be industrial societies that have done a poor job of subordinating personal or local loyalties to loyalty to the system are usually very inefficient. (Look at Latin America.) Thus an advanced industrial society can tolerate only those small-scale communities that are emasculated, tamed and made into tools of the system. [7]
53. Crowding, rapid change and the breakdown of communities have been widely recognized as sources of social problems. But we do not believe they are enough to account for the extent of the problems that are seen today.
54. A few pre-industrial cities were very large and crowded, yet their inhabitants do not seem to have suffered from psychological problems to the same extent as modern man. In America today there still are uncrowded rural areas, and we find there the same problems as in urban areas, though the problems tend to be less acute in the rural areas. Thus crowding does not seem to be the decisive factor.
55. On the growing edge of the American frontier during the 19th century, the mobility of the population probably broke down extended families and small-scale social groups to at least the same extent as these are broken down today. In fact, many nuclear families lived by choice in such isolation, having no neighbors within several miles, that they belonged to no community at all, yet they do not seem to have developed problems as a result.
56. Furthermore, change in American frontier society was very rapid and deep. A man might be born and raised in a log cabin, outside the reach of law and order and fed largely on wild meat; and by the time he arrived at old age he might be working at a regular job and living in an ordered community with effective law enforcement. This was a deeper change than that which typically occurs in the life of a modern individual, yet it does not seem to have led to psychological problems. In fact, 19th century American society had an optimistic and self-confident tone, quite unlike that of today's society. [8]
57. The difference, we argue, is that modern man has the sense (largely justified) that change is IMPOSED on him, whereas the 19th century frontiersman had the sense (also largely justified) that he created change himself, by his own choice. Thus a pioneer settled on a piece of land of his own choosing and made it into a farm through his own effort. In those days an entire county might have only a couple of hundred inhabitants and was a far more isolated and autonomous entity than a modern county is. Hence the pioneer farmer participated as a member of a relatively small group in the creation of a new, ordered community. One may well question whether the creation of this community was an improvement, but at any rate it satisfied the pioneer's need for the power process.
58. It would be possible to give other examples of societies in which there has been rapid change and/or lack of close community ties without the kind of massive behavioral aberration that is seen in today's industrial society. We contend that the most important cause of social and psychological problems in modern society is the fact that people have insufficient opportunity to go through the power process in a normal way. We don't mean to say that modern society is the only one in which the power process has been disrupted. Probably most if not all civilized societies have interfered with the power process to a greater or lesser extent. But in modern industrial society the problem has become particularly acute. Leftism, at least in its recent (mid- to late-20th century) form, is in part a symptom of deprivation with respect to the power process.
DISRUPTION OF THE POWER PROCESS IN MODERN SOCIETY
59. We divide human drives into three groups: (1) those drives that can be satisfied with minimal effort; (2) those that can be satisfied but only at the cost of serious effort; (3) those that cannot be adequately satisfied no matter how much effort one makes. The power process is the process of satisfying the drives of the second group. The more drives there are in the third group, the more there is frustration, anger, eventually defeatism, depression, etc.
60. In modern industrial society natural human drives tend to be pushed into the first and third groups, and the second group tends to consist increasingly of artificially created drives.
61. In primitive societies, physical necessities generally fall into group 2: They can be obtained, but only at the cost of serious effort. But modern society tends to guaranty the physical necessities to everyone [9] in exchange for only minimal effort, hence physical needs are pushed into group 1. (There may be disagreement about whether the effort needed to hold a job is "minimal"; but usually, in lower- to middle-level jobs, whatever effort is required is merely that of OBEDIENCE. You sit or stand where you are told to sit or stand and do what you are told to do in the way you are told to do it. Seldom do you have to exert yourself seriously, and in any case you have hardly any autonomy in work, so that the need for the power process is not well served.)
62. Social needs, such as sex, love and status, often remain in group 2 in modern society, depending on the situation of the individual. [10] But, except for people who have a particularly strong drive for status, the effort required to fulfill the social drives is insufficient to satisfy adequately the need for the power process.
63. So certain artificial needs have been created that fall into group 2, hence serve the need for the power process. Advertising and marketing techniques have been developed that make many people feel they need things that their grandparents never desired or even dreamed of. It requires serious effort to earn enough money to satisfy these artificial needs, hence they fall into group 2. (But see paragraphs 80-82.) Modern man must satisfy his need for the power process largely through pursuit of the artificial needs created by the advertising and marketing industry [11], and through surrogate activities.
64. It seems that for many people, maybe the majority, these artificial forms of the power process are insufficient. A theme that appears repeatedly in the writings of the social critics of the second half of the 20th century is the sense of purposelessness that afflicts many people in modern society. (This purposelessness is often called by other names such as "anomic" or "middle-class vacuity.") We suggest that the so-called "identity crisis" is actually a search for a sense of purpose, often for commitment to a suitable surrogate activity. It may be that existentialism is in large part a response to the purposelessness of modern life. [12] Very widespread in modern society is the search for "fulfillment." But we think that for the majority of people an activity whose main goal is fulfillment (that is, a surrogate activity) does not bring completely satisfactory fulfillment. In other words, it does not fully satisfy the need for the power process. (See paragraph 41.) That need can be fully satisfied only through activities that have some external goal, such as physical necessities, sex, love, status, revenge, etc.
65. Moreover, where goals are pursued through earning money, climbing the status ladder or functioning as part of the system in some other way, most people are not in a position to pursue their goals AUTONOMOUSLY. Most workers are someone else's employee and, as we pointed out in paragraph 61, must spend their days doing what they are told to do in the way they are told to do it. Even people who are in business for themselves have only limited autonomy. It is a chronic complaint of small-business persons and entrepreneurs that their hands are tied by excessive government regulation. Some of these regulations are doubtless unnecessary, but for the most part government regulations are essential and inevitable parts of our extremely complex society. A large portion of small business today operates on the franchise system. It was reported in the Wall Street Journal a few years ago that many of the franchise-granting companies require applicants for franchises to take a personality test that is designed to EXCLUDE those who have creativity and initiative, because such persons are not sufficiently docile to go along obediently with the franchise system. This excludes from small business many of the people who most need autonomy.
66. Today people live more by virtue of what the system does FOR them or TO them than by virtue of what they do for themselves. And what they do for themselves is done more and more along channels laid down by the system. Opportunities tend to be those that the system provides, the opportunities must be exploited in accord with rules and regulations [13], and techniques prescribed by experts must be followed if there is to be a chance of success.
67. Thus the power process is disrupted in our society through a deficiency of real goals and a deficiency of autonomy in the pursuit of goals. But it is also disrupted because of those human drives that fall into group 3: the drives that one cannot adequately satisfy no matter how much effort one makes. One of these drives is the need for security. Our lives depend on decisions made by other people; we have no control over these decisions and usually we do not even know the people who make them. ("We live in a world in which relatively few peoplesmaybe 500 or 1,000smake the important decisions"sPhilip B. Heymann of Harvard Law School, quoted by Anthony Lewis, New York Times, April 21, 1995.) Our lives depend on whether safety standards at a nuclear power plant are properly maintained; on how much pesticide is allowed to get into our food or how much pollution into our air; on how skillful (or incompetent) our doctor is; whether we lose or get a job may depend on decisions made by government economists or corporation executives; and so forth. Most individuals are not in a position to secure themselves against these threats to more [than] a very limited extent. The individual's search for security is therefore frustrated, which leads to a sense of powerlessness.
68. It may be objected that primitive man is physically less secure than modern man, as is shown by his shorter life expectancy; hence modern man suffers from less, not more than the amount of insecurity that is normal for human beings. But psychological security does not closely correspond with physical security. What makes us FEEL secure is not so much objective security as a sense of confidence in our ability to take care of ourselves. Primitive man, threatened by a fierce animal or by hunger, can fight in self-defense or travel in search of food. He has no certainty of success in these efforts, but he is by no means helpless against the things that threaten him. The modern individual on the other hand is threatened by many things against which he is helpless: nuclear accidents, carcinogens in food, environmental pollution, war, increasing taxes, invasion of his privacy by large organizations, nationwide social or economic phenomena that may disrupt his way of life.
69. It is true that primitive man is powerless against some of the things that threaten him; disease for example. But he can accept the risk of disease stoically. It is part of the nature of things, it is no one's fault, unless it is the fault of some imaginary, impersonal demon. But threats to the modern individual tend to be MAN-MADE. They are not the results of chance but are IMPOSED on him by other persons whose decisions he, as an individual, is unable to influence. Consequently he feels frustrated, humiliated and angry.
70. Thus primitive man for the most part has his security in his own hands (either as an individual or as a member of a SMALL group) whereas the security of modern man is in the hands of persons or organizations that are too remote or too large for him to be able personally to influence them. So modern man's drive for security tends to fall into groups 1 and 3; in some areas (food, shelter etc.) his security is assured at the cost of only trivial effort, whereas in other areas he CANNOT attain security. (The foregoing greatly simplifies the real situation, but it does indicate in a rough, general way how the condition of modern man differs from that of primitive man.)
71. People have many transitory drives or impulses that are necessarily frustrated in modern life, hence fall into group 3. One may become angry, but modern society cannot permit fighting. In many situations it does not even permit verbal aggression. When going somewhere one may be in a hurry, or one may be in a mood to travel slowly, but one generally has no choice but to move with the flow of traffic and obey the traffic signals. One may want to do one's work in a different way, but usually one can work only according to the rules laid down by one's employer. In many other ways as well, modern man is strapped down by a network of rules and regulations (explicit or implicit) that frustrate many of his impulses and thus interfere with the power process. Most of these regulations cannot be dispensed with, because they are necessary for the functioning of industrial society.
72. Modern society is in certain respects extremely permissive. In matters that are irrelevant to the functioning of the system we can generally do what we please. We can believe in any religion we like (as long as it does not encourage behavior that is dangerous to the system). We can go to bed with anyone we like (as long as we practice "safe sex"). We can do anything we like as long as it is UNIMPORTANT. But in all IMPORTANT matters the system tends increasingly to regulate our behavior.
73. Behavior is regulated not only through explicit rules and not only by the government. Control is often exercised through indirect coercion or through psychological pressure or manipulation, and by organizations other than the government, or by the system as a whole. Most large organizations use some form of propaganda [14] to manipulate public attitudes or behavior. Propaganda is not limited to "commercials" and advertisements, and sometimes it is not even consciously intended as propaganda by the people who make it. For instance, the content of entertainment programming is a powerful form of propaganda. An example of indirect coercion: There is no law that says we have to go to work every day and follow our employer's orders. Legally there is nothing to prevent us from going to live in the wild like primitive people or from going into business for ourselves. But in practice there is very little wild country left, and there is room in the economy for only a limited number of small business owners. Hence most of us can survive only as someone else's employee.
74. We suggest that modern man's obsession with longevity, and with maintaining physical vigor and sexual attractiveness to an advanced age, is a symptom of unfulfillment resulting from deprivation with respect to the power process. The "mid-life crisis" also is such a symptom. So is the lack of interest in having children that is fairly common in modern society but almost unheard-of in primitive societies.
75. In primitive societies life is a succession of stages. The needs and purposes of one stage having been fulfilled, there is no particular reluctance about passing on to the next stage. A young man goes through the power process by becoming a hunter, hunting not for sport or for fulfillment but to get meat that is necessary for food. (In young women the process is more complex, with greater emphasis on social power; we won't discuss that here.) This phase having been successfully passed through, the young man has no reluctance about settling down to the responsibilities of raising a family. (In contrast, some modern people indefinitely postpone having children because they are too busy seeking some kind of "fulfillment." We suggest that the fulfillment they need is adequate experience of the power processswith real goals instead of the artificial goals of surrogate activities.) Again, having successfully raised his children, going through the power process by providing them with the physical necessities, the primitive man feels that his work is done and he is prepared to accept old age (if he survives that long) and death. Many modern people, on the other hand, are disturbed by the prospect of physical deterioration and death, as is shown by the amount of effort they expend trying to maintain their physical condition, appearance and health. We argue that this is due to unfulfillment resulting from the fact that they have never put their physical powers to any practical use, have never gone through the power process using their bodies in a serious way. It is not the primitive man, who has used his body daily for practical purposes, who fears the deterioration of age, but the modern man, who has never had a practical use for his body beyond walking from his car to his house. It is the man whose need for the power process has been satisfied during his life who is best prepared to accept the end of that life.
76. In response to the arguments of this section someone will say, "Society must find a way to give people the opportunity to go through the power process." For such people the value of the opportunity is destroyed by the very fact that society gives it to them. What they need is to find or make their own opportunities. As long as the system GIVES them their opportunities it still has them on a leash. To attain autonomy they must get off that leash.
HOW SOME People adjust
77. Not everyone in industrial-technological society suffers from psychological problems. Some people even profess to be quite satisfied with society as it is. We now discuss some of the reasons why people differ so greatly in their response to modern society.
78. First, there doubtless are differences in the strength of the drive for power. Individuals with a weak drive for power may have relatively little need to go through the power process, or at least relatively little need for autonomy in the power process. These are docile types who would have been happy as plantation darkies in the Old South. (We don't mean to sneer at the "plantation darkies" of the Old South. To their credit, most of the slaves were NOT content with their servitude. We do sneer at people who ARE content with servitude.)
79. Some people may have some exceptional drive, in pursuing which they satisfy their need for the power process. For example, those who have an unusually strong drive for social status may spend their whole lives climbing the status ladder without ever getting bored with that game.
80. People vary in their susceptibility to advertising and marketing techniques. Some are so susceptible that, even if they make a great deal of money, they cannot satisfy their constant craving for the the shiny new toys that the marketing industry dangles before their eyes. So they always feel hard-pressed financially even if their income is large, and their cravings are frustrated.
81. Some people have low susceptibility to advertising and marketing techniques. These are the people who aren't interested in money. Material acquisition does not serve their need for the power process.
82. People who have medium susceptibility to advertising and marketing techniques are able to earn enough money to satisfy their craving for goods and services, but only at the cost of serious effort (putting in overtime, taking a second job, earning promotions, etc.). Thus material acquisition serves their need for the power process. But it does not necessarily follow that their need is fully satisfied. They may have insufficient autonomy in the power process (their work may consist of following orders) and some of their drives may be frustrated (e.g., security, aggression). (We are guilty of oversimplification in paragraphs 80-82 because we have assumed that the desire for material acquisition is entirely a creation of the advertising and marketing industry. Of course it's not that simple. [11]
83. Some people partly satisfy their need for power by identifying themselves with a powerful organization or mass movement. An individual lacking goals or power joins a movement or an organization, adopts its goals as his own, then works toward those goals. When some of the goals are attained, the individual, even though his personal efforts have played only an insignificant part in the attainment of the goals, feels (through his identif ication with the movement or organization) as if he had gone through the power process. This phenomenon was exploited by the fascists, nazis and communists. Our society uses it too, though less crudely. Example: Manuel Noriega was an irritant to the U.S. (goal: punish Noriega). The U.S. invaded Panama (effort) and punished Noriega (attainment of goal). Thus the U.S. went through the power process and many Americans, because of their identification with the U.S., experienced the power process vicariously. Hence the widespread public approval of the Panama invasion; it gave people a sense of power. [15] We see the same phenomenon in armies, corporations, political parties, humanitarian organizations, religious or ideological movements. In particular, leftist movements tend to attract people who are seeking to satisfy their need for power. But for most people identification with a large organization or a mass movement does not fully satisfy the need for power.
84. Another way in which people satisfy their need for the power process is through surrogate activities. As we explained in paragraphs 38-40, a surrogate activity is an activity that is directed toward an artificial goal that the individual pursues for the sake of the "fulfillment" that he gets from pursuing the goal, not because he needs to attain the goal itself. For instance, there is no practical motive for building enormous muscles, hitting a little ball into a hole or acquiring a complete series of postage stamps. Yet many people in our society devote themselves with passion to bodybuilding, golf or stamp-collecting. Some people are more "other-directed" than others, and therefore will more readily attach importance to a surrogate activity simply because the people around them treat it as important or because society tells them it is important. That is why some people get very serious about essentially trivial activities such as sports, or bridge, or chess, or arcane scholarly pursuits, whereas others who are more clear-sighted never see these things as anything but the surrogate activities that they are, and consequently never attach enough importance to them to satisfy their need for the power process in that way. It only remains to point out that in many cases a person's way of earning a living is also a surrogate activity. Not a PURE surrogate activity, since part of the motive for the activity is to gain the physical necessities and (for some people) social status and the luxuries that advertising makes them want. But many people put into their work far more effort than is necessary to earn whatever money and status they require, and this extra effort constitutes a surrogate activity. This extra effort, together with the emotional investment that accompanies it, is one of the most potent forces acting toward the continual development and perfecting of the system, with negative consequences for individual freedom (see paragraph 131). Especially, for the most creative scientists and engineers, work tends to be largely a surrogate activity. This point is so important that it deserves a separate discussion, which we shall give in a moment (paragraphs 87-92).
85. In this section we have explained how many people in modern society do satisfy their need for the power process to a greater or lesser extent. But we think that for the majority of people the need for the power process is not fully satisfied. In the first place, those who have an insatiable drive for status, or who get firmly "hooked" on a surrogate activity, or who identify strongly enough with a movement or organization to satisfy their need for power in that way, are exceptional personalities. Others are not fully satisfied with surrogate activities or by identification with an organization (see paragraphs 41, 64). In the second place, too much control is imposed by the system through explicit regulation or through socialization, which results in a deficiency of autonomy, and in frustration due to the impossibility of attaining certain goals and the necessity of restraining too many impulses.
86. But even if most people in industrial-technological society were well satisfied, we (FC) would still be opposed to that form of society, because (among other reasons) we consider it demeaning to fulfill one's need for the power process through surrogate activities or through identification with an organization, rather than through pursuit of real goals.
THE MOTIVES OF SCIENTISTS
87. Science and technology provide the most important examples of surrogate activities. Some scientists claim that they are motivated by "curiosity" or by a desire to "benefit humanity." But it is easy to see that neither of these can be the principal motive of most scientists. As for "curiosity," that notion is simply absurd. Most scientists work on highly specialized problems that are not the object of any normal curiosity. For example, is an astronomer, a mathematician or an entomologist curious about the properties of isopropyltrimethylmethane? Of course not. Only a chemist is curious about such a thing, and he is curious about it only because chemistry is his surrogate activity. Is the chemist curious about the appropriate classification of a new species of beetle? No. That question is of interest only to the entomologist, and he is interested in it only because entomology is his surrogate activity. If the chemist and the entomologist had to exert themselves seriously to obtain the physical necessities, and if that effort exercised their abilities in an interesting way but in some nonscientific pursuit, then they wouldn't give a damn about isopropyltrimethylmethane or the classification of beetles. Suppose that lack of funds for postgraduate education had led the chemist to become an insurance broker instead of a chemist. In that case he would have been very interested in insurance matters but would have cared nothing about isopropyltrimethylmethane. In any case it is not normal to put into the satisfaction of mere curiosity the amount of time and effort that scientists put into their work. The "curiosity" explanation for the scientists' motive just doesn't stand up.
88. The "benefit of humanity" explanation doesn't work any better. Some scientific work has no conceivable relation to the welfare of the human racesmost of archaeology or comparative linguistics for example. Some other areas of science present obviously dangerous possibilities. Yet scientists in these areas are just as enthusiastic about their work as those who develop vaccines or study air pollution. Consider the case of Dr. Edward Teller, who had an obvious emotional involvement in promoting nuclear power plants. Did this involvement stem from a desire to benefit humanity? If so, then why didn't Dr. Teller get emotional about other "humanitarian" causes? If he was such a humanitarian then why did he help to develop the H-bomb? As with many other scientific achievements, it is very much open to question whether nuclear power plants actually do benefit humanity. Does the cheap electricity outweigh the accumulating waste and the risk of accidents? Dr. Teller saw only one side of the question. Clearly his emotional involvement with nuclear power arose not from a desire to "benefit humanity" but from a personal fulfillment he got from his work and from seeing it put to practical use.
89. The same is true of scientists generally. With possible rare exceptions, their motive is neither curiosity nor a desire to benefit humanity but the need to go through the power process: to have a goal (a scientific problem to solve), to make an effort (research) and to attain the goal (solution of the problem.) Science is a surrogate activity because scientists work mainly for the fulfillment they get out of the work itself.
90. Of course, it's not that simple. Other motives do play a role for many scientists. Money and status for example. Some scientists may be persons of the type who have an insatiable drive for status (see paragraph 79) and this may provide much of the motivation for their work. No doubt the majority of scientists, like the majority of the general population, are more or less susceptible to advertising and marketing techniques and need money to satisfy their craving for goods and services. Thus science is not a PURE surrogate activity. But it is in large part a surrogate activity.
91. Also, science and technology constitute a power mass movement, and many scientists gratify their need for power through identification with this mass movement (see paragraph 83).
92. Thus science marches on blindly, without regard to the real welfare of the human race or to any other standard, obedient only to the psychological needs of the scientists and of the government officials and corporation executives who provide the funds for research.
THE NATURE OF FREEDOM
93. We are going to argue that industrial-technological society cannot be reformed in such a way as to prevent it from progressively narrowing the sphere of human freedom. But, because "freedom" is a word that can be interpreted in many ways, we must first make clear what kind of freedom we are concerned with.
94. By "freedom" we mean the opportunity to go through the power process, with real goals not the artificial goals of surrogate activities, and without interference, manipulation or supervision from anyone, especially from any large organization. Freedom means being in control (either as an individual or as a member of a SMALL group) of the life-and-death issues of one's existence; food, clothing, shelter and defense against whatever threats there may be in one's environment. Freedom means having power; not the power to control other people but the power to control the circumstances of one's own life. One does not have freedom if anyone else (especially a large organization) has power over one, no matter how benevolently, tolerantly and permissively that power may be exercised. It is important not to confuse freedom with mere permissiveness (see paragraph 72).
95. It is said that we live in a free society because we have a certain number of constitutionally guaranteed rights. But these are not as important as they seem. The degree of personal freedom that exists in a society is determined more by the economic and technological structure of the society than by its laws or its form of government. [16] Most of the Indian nations of New England were monarchies, and many of the cities of the Italian Renaissance were controlled by dictators. But in reading about these societies one gets the impression that they allowed far more personal freedom than our society does. In part this was because they lacked efficient mechanisms for enforcing the ruler's will: There were no modern, well-organized police forces, no rapid long-distance communications, no surveillance cameras, no dossiers of information about the lives of average citizens. Hence it was relatively easy to evade control.
96. As for our constitutional rights, consider for example that of freedom of the press. We certainly don't mean to knock that right; it is very important tool for limiting concentration of political power and for keeping those who do have political power in line by publicly exposing any misbehavior on their part. But freedom of the press is of very little use to the average citizen as an individual. The mass media are mostly under the control of large organizations that are integrated into the system. Anyone who has a little money can have something printed, or can distribute it on the Internet or in some such way, but what he has to say will be swamped by the vast volume of material put out by the media, hence it will have no practical effect. To make an impression on society with words is therefore almost impossible for most individuals and small groups. Take us (FC) for example. If we had never done anything violent and had submitted the present writings to a publisher, they probably would not have been accepted. If they had been been accepted and published, they probably would not have attracted many readers, because it's more fun to watch the entertainment put out by the media than to read a sober essay. Even if these writings had had many readers, most of these readers would soon have forgotten what they had read as their minds were flooded by the mass of material to which the media expose them. In order to get our message before the public with some chance of making a lasting impression, we've had to kill people.
97. Constitutional rights are useful up to a point, but they do not serve to guarantee much more than what might be called the bourgeois conception of freedom. According to the bourgeois conception, a "free" man is essentially an element of a social machine and has only a certain set of prescribed and delimited freedoms; freedoms that are designed to serve the needs of the social machine more than those of the individual. Thus the bourgeois's "free" man has economic freedom because that promotes growth and progress; he has freedom of the press because public criticism restrains misbehavior by political leaders; he has a right to a fair trial because imprisonment at the whim of the powerful would be bad for the system. This was clearly the attitude of Simon Bolivar. To him, people deserved liberty only if they used it to promote progress (progress as conceived by the bourgeois). Other bourgeois thinkers have taken a similar view of freedom as a mere means to collective ends. Chester C. Tan, "Chinese Political Thought in the Twentieth Century," page 202, explains the philosophy of the Kuomintang leader Hu Han-min: "An individual is granted rights because he is a member of society and his community life requires such rights. By community Hu meant the whole society of the nation." And on page 259 Tan states that according to Carsum Chang (Chang Chun-mai, head of the State Socialist Party in China) freedom had to be used in the interest of the state and of the people as a whole. But what kind of freedom does one have if one can use it only as someone else prescribes? FC's conception of freedom is not that of Bolivar, Hu, Chang or other bourgeois theorists. The trouble with such theorists is that they have made the development and application of social theories their surrogate activity. Consequently the theories are designed to serve the needs of the theorists more than the needs of any people who may be unlucky enough to live in a society on which the theories are imposed.
98. One more point to be made in this section: It should not be assumed that a person has enough freedom just because he SAYS he has enough. Freedom is restricted in part by psychological controls of which people are unconscious, and moreover many people's ideas of what constitutes freedom are governed more by social convention than by their real needs. For example, it's likely that many leftists of the oversocialized type would say that most people, including themselves, are socialized too little rather than too much, yet the oversocialized leftist pays a heavy psychological price for his high level of socialization.
SOME PRINCIPLES OF HISTORY
99. Think of history as being the sum of two components: an erratic component that consists of unpredictable events that follow no discernible pattern, and a regular component that consists of long-term historical trends. Here we are concerned with the long-term trends.
100. FIRST PRINCIPLE. If a SMALL change is made that affects a long-term historical trend, then the effect of that change will almost always be transitorysthe trend will soon revert to its original state. (Example: A reform movement designed to clean up political corruption in a society rarely has more than a short-term effect; sooner or later the reformers relax and corruption creeps back in. The level of political corruption in a given society tends to remain constant, or to change only slowly with the evolution of the society. Normally, a political cleanup will be permanent only if accompanied by widespread social changes; a SMALL change in the society won't be enough.) If a small change in a long-term historical trend appears to be permanent, it is only because the change acts in the direction in which the trend is already moving, so that the trend is not altered by only pushed a step ahead.
101. The first principle is almost a tautology. If a trend were not stable with respect to small changes, it would wander at random rather than following a definite direction; in other words it would not be a long-term trend at all.
102. SECOND PRINCIPLE. If a change is made that is sufficiently large to alter permanently a long-term historical trend, then it will alter the society as a whole. In other words, a society is a system in which all parts are interrelated, and you can't permanently change any important part without changing all other parts as well.
103. THIRD PRINCIPLE. If a change is made that is large enough to alter permanently a long-term trend, then the consequences for the society as a whole cannot be predicted in advance. (Unless various other societies have passed through the same change and have all experienced the same consequences, in which case one can predict on empirical grounds that another society that passes through the same change will be like to experience similar consequences.)
104. FOURTH PRINCIPLE. A new kind of society cannot be designed on paper. That is, you cannot plan out a new form of society in advance, then set it up and expect it to function as it was designed to do.
105. The third and fourth principles result from the complexity of human societies. A change in human behavior will affect the economy of a society and its physical environment; the economy will affect the environment and vice versa, and the changes in the economy and the environment will affect human behavior in complex, unpredictable ways; and so forth. The network of causes and effects is far too complex to be untangled and understood.
106. FIFTH PRINCIPLE. People do not consciously and rationally choose the form of their society. Societies develop through processes of social evolution that are not under rational human control.
107. The fifth principle is a consequence of the other four.
108. To illustrate: By the first principle, generally speaking an attempt at social reform either acts in the direction in which the society is developing anyway (so that it merely accelerates a change that would have occurred in any case) or else it has only a transitory effect, so that the society soon slips back into its old groove. To make a lasting change in the direction of development of any important aspect of a society, reform is insufficient and revolution is required. (A revolution does not necessarily involve an armed uprising or the overthrow of a government.) By the second principle, a revolution never changes only one aspect of a society, it changes the whole society; and by the third principle changes occur that were never expected or desired by the revolutionaries. By the fourth principle, when revolutionaries or utopians set up a new kind of society, it never works out as planned.
109. The American Revolution does not provide a counterexample. The American "Revolution" was not a revolution in our sense of the word, but a war of independence followed by a rather far-reaching political reform. The Founding Fathers did not change the direction of development of American society, nor did they aspire to do so. They only freed the development of American society from the retarding effect of British rule. Their political reform did not change any basic trend, but only pushed American political culture along its natural direction of development. British society, of which American society was an offshoot, had been moving for a long time in the direction of representative democracy. And prior to the War of Independence the Americans were already practicing a significant degree of representative democracy in the colonial assemblies. The political system established by the Constitution was modeled on the British system and on the colonial assemblies. With major alteration, to be suresthere is no doubt that the Founding Fathers took a very important step. But it was a step along the road that English-speaking world was already traveling. The proof is that Britain and all of its colonies that were populated predominantly by people of British descent ended up with systems of representative democracy essentially similar to that of the United States. If the Founding Fathers had lost their nerve and declined to sign the Declaration of Independence, our way of life today would not have been significantly different. Maybe we would have had somewhat closer ties to Britain, and would have had a Parliament and Prime Minister instead of a Congress and President. No big deal. Thus the American Revolution provides not a counterexample to our principles but a good illustration of them.
110. Still, one has to use common sense in applying the principles. They are expressed in imprecise language that allows latitude for interpretation, and exceptions to them can be found. So we present these principles not as inviolable laws but as rules of thumb, or guides to thinking, that may provide a partial antidote to naive ideas about the future of society. The principles should be borne constantly in mind, and whenever one reaches a conclusion that conflicts with them one should carefully reexamine one's thinking and retain the conclusion only if one has good, solid reasons for doing so.
INDUSTRIAL-TECHNOLOGICAL SOCIETY CANNOT BE REFORMED
111. The foregoing principles help to show how hopelessly difficult it would be to reform the industrial system in such a way as to prevent it from progressively narrowing our sphere of freedom. There has been a consistent tendency, going back at least to the Industrial Revolution for technology to strengthen the system at a high cost in individual freedom and local autonomy. Hence any change designed to protect freedom from technology would be contrary to a fundamental trend in the development of our society. Consequently, such a change either would be a transitory onessoon swamped by the tide of historysor, if large enough to be permanent would alter the nature of our whole society. This by the first and second principles. Moreover, since society would be altered in a way that could not be predicted in advance (third principle) there would be great risk. Changes large enough to make a lasting difference in favor of freedom would not be initiated because it would be realized that they would gravely disrupt the system. So any attempts at reform would be too timid to be effective. Even if changes large enough to make a lasting difference were initiated, they would be retracted when their disruptive effects became apparent. Thus, permanent changes in favor of freedom could be brought about only by persons prepared to accept radical, dangerous and unpredictable alteration of the entire system. In other words by revolutionaries, not reformers.
112. People anxious to rescue freedom without sacrificing the supposed benefits of technology will suggest naive schemes for some new form of society that would reconcile freedom with technology. Apart from the fact that people who make such suggestions seldom propose any practical means by which the new form of society could be set up in the first place, it follows from the fourth principle that even if the new form of society could be once established, it either would collapse or would give results very different from those expected.
113. So even on very general grounds it seems highly improbable that any way of changing society could be found that would reconcile freedom with modern technology. In the next few sections we will give more specific reasons for concluding that freedom and technological progress are incompatible.
RESTRICTION OF FREEDOM IS UNAVOIDABLE IN INDUSTRIAL SOCIETY
114. As explained in paragraphs 65-67, 70-73, modern man is strapped down by a network of rules and regulations, and his fate depends on the actions of persons remote from him whose decisions he cannot influence. This is not accidental or a result of the arbitrariness of arrogant bureaucrats. It is necessary and inevitable in any technologically advanced society. The system HAS TO regulate human behavior closely in order to function. At work people have to do what they are told to do, otherwise production would be thrown into chaos. Bureaucracies HAVE TO be run according to rigid rules. To allow any substantial personal discretion to lower-level bureaucrats would disrupt the system and lead to charges of unfairness due to differences in the way individual bureaucrats exercised their discretion. It is true that some restrictions on our freedom could be eliminated, but GENERALLY SPEAKING the regulation of our lives by large organizations is necessary for the functioning of industrial-technological society. The result is a sense of powerlessness on the part of the average person. It may be, however, that formal regulations will tend increasingly to be replaced by psychological tools that make us want to do what the system requires of us. (Propaganda [14], educational techniques, "mental health" programs, etc.)
115. The system HAS TO force people to behave in ways that are increasingly remote from the natural pattern of human behavior. For example, the system needs scientists, mathematicians and engineers. It can't function without them. So heavy pressure is put on children to excel in these fields. It isn't natural for an adolescent human being to spend the bulk of his time sitting at a desk absorbed in study. A normal adolescent wants to spend his time in active contact with the real world. Among primitive peoples the things that children are trained to do tend to be in reasonable harmony with natural human impulses. Among the American Indians, for example, boys were trained in active outdoor pursuits just the sort of thing that boys like. But in our society children are pushed into studying technical subjects, which most do grudgingly.
116. Because of the constant pressure that the system exerts to modify human behavior, there is a gradual increase in the number of people who cannot or will nottadjust to society's requirements: welfare leeches, youth-gang members, cultists, anti-government rebels, radical environmentalist saboteurs, dropouts and resisters of various kinds.
117. In any technologically advanced society the individual's fate MUST depend on decisions that he personally cannot influence to any great extent. A technological society cannot be broken down into small, autonomous communities, because production depends on the cooperation of very large numbers of people and machines. Such a society MUST be highly organized and decisions HAVE TO be made that affect very large numbers of people. When a decision affects, say, a million people, then each of the affected individuals has, on the average, only a one-millionth share in making the decision. What usually happens in practice is that decisions are made by public officials or corporation executives, or by technical specialists, but even when the public votes on a decision the number of voters ordinarily is too large for the vote of any one individual to be significant. [17] Thus most individuals are unable to influence measurably the major decisions that affect their lives. There is no conceivable way to remedy this in a technologically advanced society. The system tries to "solve" this problem by using propaganda to make people WANT the decisions that have been made for them, but even if this "solution" were completely successful in making people feel better, it would be demeaning.
118. Conservatives and some others advocate more "local autonomy." Local communities once did have autonomy, but such autonomy becomes less and less possible as local communities become more enmeshed with and dependent on large-scale systems like public utilities, computer networks, highway systems, the mass communications media, the modern health care system. Also operating against autonomy is the fact that technology applied in one location often affects people at other locations far way. Thus pesticide or chemical use near a creek may contaminate the water supply hundreds of miles downstream, and the greenhouse effect affects the whole world.
119. The system does not and cannot exist to satisfy human needs. Instead, it is human behavior that has to be modified to fit the needs of the system. This has nothing to do with the political or social ideology that may pretend to guide the technological system. It is the fault of technology, because the system is guided not by ideology but by technical necessity. [18] Of course the system does satisfy many human needs, but generally speaking it does this only to the extend that it is to the advantage of the system to do it. It is the needs of the system that are paramount, not those of the human being. For example, the system provides people with food because the system couldn't function if everyone starved; it attends to people's psychological needs whenever it can CONVENIENTLY do so, because it couldn't function if too many people became depressed or rebellious. But the system, for good, solid, practical reasons, must exert constant pressure on people to mold their behavior to the needs of the system. To much waste accumulating? The government, the media, the educational system, environmentalists, everyone inundates us with a mass of propaganda about recycling. Need more technical personnel? A chorus of voices exhorts kids to study science. No one stops to ask whether it is inhumane to force adolescents to spend the bulk of their time studying subjects most of them hate. When skilled workers are put out of a job by technical advances and have to undergo "retraining," no one asks whether it is humiliating for them to be pushed around in this way. It is simply taken for granted that everyone must bow to technical necessity. and for good reason: If human needs were put before technical necessity there would be economic problems, unemployment, shortages or worse. The concept of "mental health" in our society is defined largely by the extent to which an individual behaves in accord with the needs of the system and does so without showing signs of stress.
120. Efforts to make room for a sense of purpose and for autonomy within the system are no better than a joke. For example, one company, instead of having each of its employees assemble only one section of a catalogue, had each assemble a whole catalogue, and this was supposed to give them a sense of purpose and achievement. Some companies have tried to give their employees more autonomy in their work, but for practical reasons this usually can be done only to a very limited extent, and in any case employees are never given autonomy as to ultimate goalsstheir "autonomous" efforts can never be directed toward goals that they select personally, but only toward their employer's goals, such as the survival and growth of the company. Any company would soon go out of business if it permitted its employees to act otherwise. Similarly, in any enterprise within a socialist system, workers must direct their efforts toward the goals of the enterprise, otherwise the enterprise will not serve its purpose as part of the system. Once again, for purely technical reasons it is not possible for most individuals or small groups to have much autonomy in industrial society. Even the small-business owner commonly has only limited autonomy. Apart from the necessity of government regulation, he is restricted by the fact that he must fit into the economic system and conform to its requirements. For instance, when someone develops a new technology, the small-business person often has to use that technology whether he wants to or not, in order to remain competitive.
THE 'BAD' PARTS OF TECHNOLOGY CANNOT BE SEPARATED FROM THE 'GOOD' PARTS
121. A further reason why industrial society cannot be reformed in favor of freedom is that modern technology is a unified system in which all parts are dependent on one another. You can't get rid of the "bad" parts of technology and retain only the "good" parts. Take modern medicine, for example. Progress in medical science depends on progress in chemistry, physics, biology, computer science and other fields. Advanced medical treatments require expensive, high-tech equipment that can be made available only by a technologically progressive, economically rich society. Clearly you can't have much progress in medicine without the whole technological system and everything that goes with it.
122. Even if medical progress could be maintained without the rest of the technological system, it would by itself bring certain evils. Suppose for example that a cure for diabetes is discovered. People with a genetic tendency to diabetes will then be able to survive and reproduce as well as anyone else. Natural selection against genes for diabetes will cease and such genes will spread throughout the population. (This may be occurring to some extent already, since diabetes, while not curable, can be controlled through use of insulin.) The same thing will happen with many other diseases susceptibility to which is affected by genetic degradation of the population. The only solution will be some sort of eugenics program or extensive genetic engineering of human beings, so that man in the future will no longer be a creation of nature, or of chance, or of God (depending on your religious or philosophical opinions), but a manufactured product.
123. If you think that big government interferes in your life too much NOW, just wait till the government starts regulating the genetic constitution of your children. Such regulation will inevitably follow the introduction of genetic engineering of human beings, because the consequences of unregulated genetic engineering would be disastrous. [19]
124. The usual response to such concerns is to talk about "medical ethics." But a code of ethics would not serve to protect freedom in the face of medical progress; it would only make matters worse. A code of ethics applicable to genetic engineering would be in effect a means of regulating the genetic constitution of human beings. Somebody (probably the upper-middle class, mostly) would decide that such and such applications of genetic engineering were "ethical" and others were not, so that in effect they would be imposing their own values on the genetic constitution of the population at large. Even if a code of ethics were chosen on a completely democratic basis, the majority would be imposing their own values on any minorities who might have a different idea of what constituted an "ethical" use of genetic engineering. The only code of ethics that would truly protect freedom would be one that prohibited ANY genetic engineering of human beings, and you can be sure that no such code will ever be applied in a technological society. No code that reduced genetic engineering to a minor role could stand up for long, because the temptation presented by the immense power of biotechnology would be irresistible, especially since to the majority of people many of its applications will seem obviously and unequivocally good (eliminating physical and mental diseases, giving people the abilities they need to get along in today's world). Inevitably, genetic engineering will be used extensively, but only in ways consistent with the needs of the industrial-technological system. [20]
TECHNOLOGY IS A MORE POWERFUL SOCIAL FORCE THAN THE ASPIRATION FOR FREEDOM
125. It is not possible to make a LASTING compromise between technology and freedom, because technology is by far the more powerful social force and continually encroaches on freedom through REPEATED compromises. Imagine the case of two neighbors, each of whom at the outset owns the same amount of land, but one of whom is more powerful than the other. The powerful one demands a piece of the other's land. The weak one refuses. The powerful one says, "OK, let's compromise. Give me half of what I asked." The weak one has little choice but to give in. Some time later the powerful neighbor demands another piece of land, again there is a compromise, and so forth. By forcing a long series of compromises on the weaker man, the powerful one eventually gets all of his land. So it goes in the conflict between technology and freedom.
126. Let us explain why technology is a more powerful social force than the aspiration for freedom.
127. A technological advance that appears not to threaten freedom often turns out to threaten it very seriously later on. For example, consider motorized transport. A walking man formerly could go where he pleased, go at his own pace without observing any traffic regulations, and was independent of technological support-systems. When motor vehicles were introduced they appeared to increase man's freedom. They took no freedom away from the walking man, no one had to have an automobile if he didn't want one, and anyone who did choose to buy an automobile could travel much faster and farther than a walking man. But the introduction of motorized transport soon changed society in such a way as to restrict greatly man's freedom of locomotion. When automobiles became numerous, it became necessary to regulate their use extensively. In a car, especially in densely populated areas, one cannot just go where one likes at one's own pace one's movement is governed by the flow of traffic and by various traffic laws. One is tied down by various obligations: license requirements, driver test, renewing registration, insurance, maintenance required for safety, monthly payments on purchase price. Moreover, the use of motorized transport is no longer optional. Since the introduction of motorized transport the arrangement of our cities has changed in such a way that the majority of people no longer live within walking distance of their place of employment, shopping areas and recreational opportunities, so that they HAVE TO depend on the automobile for transportation. Or else they must use public transportation, in which case they have even less control over their own movement than when driving a car. Even the walker's freedom is now greatly restricted. In the city he continually has to stop to wait for traffic lights that are designed mainly to serve auto traffic. In the country, motor traffic makes it dangerous and unpleasant to walk along the highway. (Note this important point that we have just illustrated with the case of motorized transport: When a new item of technology is introduced as an option that an individual can accept or not as he chooses, it does not necessarily REMAIN optional. In many cases the new technology changes society in such a way that people eventually find themselves FORCED to use it.)
128. While technological progress AS A WHOLE continually narrows our sphere of freedom, each new technical advance CONSIDERED BY ITSELF appears to be desirable. Electricity, indoor plumbing, rapid long-distance communications ... how could one argue against any of these things, or against any other of the innumerable technical advances that have made modern society? It would have been absurd to resist the introduction of the telephone, for example. It offered many advantages and no disadvantages. Yet, as we explained in paragraphs 59-76, all these technical advances taken together have created a world in which the average man's fate is no longer in his own hands or in the hands of his neighbors and friends, but in those of politicians, corporation executives and remote, anonymous technicians and bureaucrats whom he as an individual has no power to influence. [21] The same process will continue in the future. Take genetic engineering, for example. Few people will resist the introduction of a genetic technique that eliminates a hereditary disease. It does no apparent harm and prevents much suffering. Yet a large number of genetic improvements taken together will make the human being into an engineered product rather than a free creation of chance (or of God, or whatever, depending on your religious beliefs).
129. Another reason why technology is such a powerful social force is that, within the context of a given society, technological progress marches in only one direction; it can never be reversed. Once a technical innovation has been introduced, people usually become dependent on it, so that they can never again do without it, unless it is replaced by some still more advanced innovation. Not only do people become dependent as individuals on a new item of technology, but, even more, the system as a whole becomes dependent on it. (Imagine what would happen to the system today if computers, for example, were eliminated.) Thus the system can move in only one direction, toward greater technologization. Technology repeatedly forces freedom to take a step back, but technology can never take a step backsshort of the overthrow of the whole technological system.
130. Technology advances with great rapidity and threatens freedom at many different points at the same time (crowding, rules and regulations, increasing dependence of individuals on large organizations, propaganda and other psychological techniques, genetic engineering, invasion of privacy through surveillance devices and computers, etc.). To hold back any ONE of the threats to freedom would require a long and difficult social struggle. Those who want to protect freedom are overwhelmed by the sheer number of new attacks and the rapidity with which they develop, hence they become apathetic and no longer resist. To fight each of the threats separately would be futile. Success can be hoped for only by fighting the technological system as a whole; but that is revolution, not reform.
131. Technicians (we use this term in its broad sense to describe all those who perform a specialized task that requires training) tend to be so involved in their work (their surrogate activity) that when a conflict arises between their technical work and freedom, they almost always decide in favor of their technical work. This is obvious in the case of scientists, but it also appears elsewhere: Educators, humanitarian groups, conservation organizations do not hesitate to use propaganda or other psychological techniques to help them achieve their laudable ends. Corporations and government agencies, when they find it useful, do not hesitate to collect information about individuals without regard to their privacy. Law enforcement agencies are frequently inconvenienced by the constitutional rights of suspects and often of completely innocent persons, and they do whatever they can do legally (or sometimes illegally) to restrict or circumvent those rights. Most of these educators, government officials and law officers believe in freedom, privacy and constitutional rights, but when these conflict with their work, they usually feel that their work is more important.
132. It is well known that people generally work better and more persistently when striving for a reward than when attempting to avoid a punishment or negative outcome. Scientists and other technicians are motivated mainly by the rewards they get through their work. But those who oppose technological invasions of freedom are working to avoid a negative outcome, consequently there are few who work persistently and well at this discouraging task. If reformers ever achieved a signal victory that seemed to set up a solid barrier against further erosion of freedom through technical progress, most would tend to relax and turn their attention to more agreeable pursuits. But the scientists would remain busy in their laboratories, and technology as it progresses would find ways, in spite of any barriers, to exert more and more control over individuals and make them always more dependent on the system.
133. No social arrangements, whether laws, institutions, customs or ethical codes, can provide permanent protection against technology. History shows that all social arrangements are transitory; they all change or break down eventually. But technological advances are permanent within the context of a given civilization. Suppose for example that it were possible to arrive at some social arrangements that would prevent genetic engineering from being applied to human beings, or prevent it from being applied in such a way as to threaten freedom and dignity. Still, the technology would remain waiting. Sooner or later the social arrangement would break down. Probably sooner, given the pace of change in our society. Then genetic engineering would begin to invade our sphere of freedom, and this invasion would be irreversible (short of a breakdown of technological civilization itself). Any illusions about achieving anything permanent through social arrangements should be dispelled by what is currently happening with environmental legislation. A few years ago its seemed that there were secure legal barriers preventing at least SOME of the worst forms of environmental degradation. A change in the political wind, and those barriers begin to crumble.
134. For all of the foregoing reasons, technology is a more powerful social force than the aspiration for freedom. But this statement requires an important qualification. It appears that during the next several decades the industrial-technological system will be undergoing severe stresses due to economic and environmental problems, and especially due to problems of human behavior (alienation, rebellion, hostility, a variety of social and psychological difficulties). We hope that the stresses through which the system is likely to pass will cause it to break down, or at least will weaken it sufficiently so that a revolution against it becomes possible. If such a revolution occurs and is successful, then at that particular moment the aspiration for freedom will have proved more powerful than technology.
135. In paragraph 125 we used an analogy of a weak neighbor who is left destitute by a strong neighbor who takes all his land by forcing on him a series of compromises. But suppose now that the strong neighbor gets sick, so that he is unable to defend himself. The weak neighbor can force the strong one to give him his land back, or he can kill him. If he lets the strong man survive and only forces him to give the land back, he is a fool, because when the strong man gets well he will again take all the land for himself. The only sensible alternative for the weaker man is to kill the strong one while he has the chance. In the same way, while the industrial system is sick we must destroy it. If we compromise with it and let it recover from its sickness, it will eventually wipe out all of our freedom.
SIMPLER SOCIAL PROBLEMS HAVE PROVED INTRACTABLE
136. If anyone still imagines that it would be possible to reform the system in such a way as to protect freedom from technology, let him consider how clumsily and for the most part unsuccessfully our society has dealt with other social problems that are far more simple and straightforward. Among other things, the system has failed to stop environmental degradation, political corruption, drug trafficking or domestic abuse.
137. Take our environmental problems, for example. Here the conflict of values is straightforward: economic expedience now versus saving some of our natural resources for our grandchildren. [22] But on this subject we get only a lot of blather and obfuscation from the people who have power, and nothing like a clear, consistent line of action, and we keep on piling up environmental problems that our grandchildren will have to live with. Attempts to resolve the environmental issue consist of struggles and compromises between different factions, some of which are ascendant at one moment, others at another moment. The line of struggle changes with the shifting currents of public opinion. This is not a rational process, nor is it one that is likely to lead to a timely and successful solution to the problem. Major social problems, if they get "solved" at all, are rarely or never solved through any rational, comprehensive plan. They just work themselves out through a process in which various competing groups pursuing their own (usually short-term) self-interest [23] arrive (mainly by luck) at some more or less stable modus vivendi. In fact, the principles we formulated in paragraphs 100-106 make it seem doubtful that rational, long-term social planning can EVER be successful.
138. Thus it is clear that the human race has at best a very limited capacity for solving even relatively straightforward social problems. How then is it going to solve the far more difficult and subtle problem of reconciling freedom with technology? Technology presents clear-cut material advantages, whereas freedom is an abstraction that means different things to different people, and its loss is easily obscured by propaganda and fancy talk.
139. And note this important difference: It is conceivable that our environmental problems (for example) may some day be settled through a rational, comprehensive plan, but if this happens it will be only because it is in the long-term interest of the system to solve these problems. But it is NOT in the interest of the system to preserve freedom or small-group autonomy. On the contrary, it is in the interest of the system to bring human behavior under control to the greatest possible extent. [24] Thus, while practical considerations may eventually force the system to take a rational, prudent approach to environmental problems, equally practical considerations will force the system to regulate human behavior ever more closely (preferably by indirect means that will disguise the encroachment on freedom). This isn't just our opinion. Eminent social scientists (e.g. James Q. Wilson) have stressed the importance of "socializing" people more effectively.
REVOLUTION IS EASIER THAN REFORM
140. We hope we have convinced the reader that the system cannot be reformed in such a way as to reconcile freedom with technology. The only way out is to dispense with the industrial-technological system altogether. This implies revolution, not necessarily an armed uprising, but certainly a radical and fundamental change in the nature of society.
141. People tend to assume that because a revolution involves a much greater change than reform does, it is more difficult to bring about than reform is. Actually, under certain circumstances revolution is much easier than reform. The reason is that a revolutionary movement can inspire an intensity of commitment that a reform movement cannot inspire. A reform movement merely offers to solve a particular social problem. A revolutionary movement offers to solve all problems at one stroke and create a whole new world; it provides the kind of ideal for which people will take great risks and make great sacrifices. For this reasons it would be much easier to overthrow the whole technological system than to put effective, permanent restraints on the development or application of any one segment of technology, such as genetic engineering, for example. Not many people will devote themselves with single-minded passion to imposing and maintaining restraints on genetic engineering, but under suitable conditions large numbers of people may devote themselves passionately to a revolution against the industrial-technological system. As we noted in paragraph 132, reformers seeking to limit certain aspects of technology would be working to avoid a negative outcome. But revolutionaries work to gain a powerful rewardsfulfillment of their revolutionary visionsand therefore work harder and more persistently than reformers do.
142. Reform is always restrained by the fear of painful consequences if changes go too far. But once a revolutionary fever has taken hold of a society, people are willing to undergo unlimited hardships for the sake of their revolution. This was clearly shown in the French and Russian Revolutions. It may be that in such cases only a minority of the population is really committed to the revolution, but this minority is sufficiently large and active so that it becomes the dominant force in society. We will have more to say about revolution in paragraphs 180-205.
CONTROL OF HUMAN BEHAVIOR
143. Since the beginning of civilization, organized societies have had to put pressures on human beings of the sake of the functioning of the social organism. The kinds of pressures vary greatly from one society to another. Some of the pressures are physical (poor diet, excessive labor, environmental pollution), some are psychological (noise, crowding, forcing human behavior into the mold that society requires). In the past, human nature has been approximately constant, or at any rate has varied only within cer tain bounds. Consequently, societies have been able to push people only up to certain limits. When the limit of human endurance has been passed, things start going wrong: rebellion, or crime, or corruption, or evasion of work, or depression and other mental problems, or an elevated death rate, or a declining birth rate or something else, so that either the society breaks down, or its functioning becomes too inefficient and it is (quickly or gradually, through conquest, attrition or evolution) replaced by some more efficient form of society. [25]
144. Thus human nature has in the past put certain limits on the development of societies. People could be pushed only so far and no farther. But today this may be changing, because modern technology is developing ways of modifying human beings.
145. Imagine a society that subjects people to conditions that make them terribly unhappy, then gives them drugs to take away their unhappiness. Science fiction? It is already happening to some extent in our own society. It is well known that the rate of clinical depression has been greatly increasing in recent decades. We believe that this is due to disruption of the power process, as explained in paragraphs 59-76. But even if we are wrong, the increasing rate of depression is certainly the result of SOME conditions that exist in today's society. Instead of removing the conditions that make people depressed, modern society gives them antidepressant drugs. In effect, antidepressants are a means of modifying an individual's internal state in such a way as to enable him to tolerate social conditions that he would otherwise find intolerable. (Yes, we know that depression is often of purely genetic origin. We are referring here to those cases in which environment plays the predominant role.)
146. Drugs that affect the mind are only one example of the new methods of controlling human behavior that modern society is developing. Let us look at some of the other methods.
147. To start with, there are the techniques of surveillance. Hidden video cameras are now used in most stores and in many other places, computers are used to collect and process vast amounts of information about individuals. Information so obtained greatly increases the effectiveness of physical coercion (i.e., law enforcement). [26] Then there are the methods of propaganda, for which the mass communication media provide effective vehicles. Efficient techniques have been developed for winning elections, selling products, influencing public opinion. The entertainment industry serves as an important psychological tool of the system, possibly even when it is dishing out large amounts of sex and violence. Entertainment provides modern man with an essential means of escape. While absorbed in television, videos, etc., he can forget stress, anxiety, frustration, dissatisfaction. Many primitive peoples, when they don't have work to do, are quite content to sit for hours at a time doing nothing at all, because they are at peace with themselves and their world. But most modern people must be constantly occupied or entertained, otherwise they get "bored," i.e., they get fidgety, uneasy, irritable.
148. Other techniques strike deeper than the foregoing. Education is no longer a simple affair of paddling a kid's behind when he doesn't know his lessons and patting him on the head when he does know them. It is becoming a scientific technique for controlling the child's development. Sylvan Learning Centers, for example, have had great success in motivating children to study, and psychological techniques are also used with more or less success in many conventional schools. "Parenting" techniques that are taught to parents are designed to make children accept fundamental values of the system and behave in ways that the system finds desirable. "Mental health" programs, "intervention" techniques, psychotherapy and so forth are ostensibly designed to benefit individuals, but in practice they usually serve as methodsfor inducing individuals to think and behave as the system requires. (There is no contradiction here; an individual whose attitudes or behavior bring him into conflict with the system is up against a force that is too powerful for him to conquer or escape from, hence he is likely to suffer from stress, frustration, defeat. His path will be much easier if he thinks and behaves as the system requires. In that sense the system is acting for the benefit of the individual when it brainwashes him into conformity.) Child abuse in its gross and obvious forms is disapproved in most if not all cultures. Tormenting a child for a trivial reason or no reason at all is something that appalls almost everyone. But many psychologists interpret the concept of abuse much more broadly. Is spanking, when used as part of a rational and consistent system of discipline, a form of abuse? The question will ultimately be decided by whether or not spanking tends to produce behavior that makes a person fit in well with the existing system of society. In practice, the word "abuse" tends to be interpreted to include any method of child-rearing that produces behavior inconvenient for the system. Thus, when they go beyond the prevention of obvious, senseless cruelty, programs for preventing "child abuse" are directed toward the control of human behavior on behalf of the system.
149. Presumably, research will continue to increase the effectiveness of psychological techniques for controlling human behavior. But we think it is unlikely that psychological techniques alone will be sufficient to adjust human beings to the kind of society that technology is creating. Biological methods probably will have to be used. We have already mentioned the use of drugs in this connection. Neurology may provide other avenues for modifying the human mind. Genetic engineering of human beings is already beginning to occur in the form of "gene therapy," and there is no reason to assume that such methods will not eventually be used to modify those aspects of the body that affect mental functioning.
150. As we mentioned in paragraph 134, industrial society seems likely to be entering a period of severe stress, due in part to problems of human behavior and in part to economic and environmental problems. And a considerable proportion of the system's economic and environmental problems result from the way human beings behave. Alienation, low self-esteem, depression, hostility, rebellion; children who won't study, youth gangs, illegal drug use, rape, child abuse, other crimes, unsafe sex, teen pregnancy, population growth, political corruption, race hatred, ethnic rivalry, bitter ideological conflict (e.g., pro-choice vs. pro-life), political extremism, terrorism, sabotage, anti-government groups, hate groups. All these threaten the very survival of the system. The system will therefore be FORCED to use every practical means of controlling human behavior.
151. The social disruption that we see today is certainly not the result of mere chance. It can only be a result of the conditions of life that the system imposes on people. (We have argued that the most important of these conditions is disruption of the power process.) If the systems succeeds in imposing sufficient control over human behavior to assure its own survival, a new watershed in human history will have been passed. Whereas formerly the limits of human endurance have imposed limits on the development of societies (as we explained in paragraphs 143, 144), industrial-technological society will be able to pass those limits by modifying human beings, whether by psychological methods or biological methods or both. In the future, social systems will not be adjusted to suit the needs of human beings. Instead, human being will be adjusted to suit the needs of the system. [27]
152. Generally speaking, technological control over human behavior will probably not be introduced with a totalitarian intention or even through a conscious desire to restrict human freedom. [28] Each new step in the assertion of control over the humanmind will be taken as a rational response to a problem that faces society, such as curing alcoholism, reducing the crime rate or inducing young people to study science and engineering. In many cases there will be a humanitarian justification. For example, when a psychiatrist prescribes an anti-depressant for a depressed patient, he is clearly doing that individual a favor. It would be inhumane to withhold the drug from someone who needs it. When parents send their children to Sylvan Learning Centers to have them manipulated into becoming enthusiastic about their studies, they do so from concern for their children's welfare. It may be that some of these parents wish that one didn't have to have specialized training to get a job and that their kid didn't have to be brainwashed into becoming a computer nerd. But what can they do? They can't change society, and their child may be unemployable if he doesn't have certain skills. So they send him to Sylvan.
153. Thus control over human behavior will be introduced not by a calculated decision of the authorities but through a process of social evolution (RAPID evolution, however). The process will be impossible to resist, because each advance, considered by itself, will appear to be beneficial, or at least the evil involved in making the advance will appear to be beneficial, or at least the evil involved in making the advance will seem to be less than that which would result from not making it (see paragraph 127). Propaganda for example is used for many good purposes, such as discouraging child abuse or race hatred. [14] Sex education is obviously useful, yet the effect of sex education (to the extent that it is successful) is to take the shaping of sexual attitudes away from the family and put it into the hands of the state as represented by the public school system.
154. Suppose a biological trait is discovered that increases the likelihood that a child will grow up to be a criminal, and suppose some sort of gene therapy can remove this trait. [29] Of course most parents whose children possess the trait will have them undergo the therapy. It would be inhumane to do otherwise, since the child would probably have a miserable life if he grew up to be a criminal. But many or most primitive societies have a low crime rate in comparison with that of our society, even though they have neither high-tech methods of child-rearing nor harsh systems of punishment. Since there is no reason to suppose that more modern men than primitive men have innate predatory tendencies, the high crime rate of our society must be due to the pressures that modern conditions put on people, to which many cannot or will not adjust. Thus a treatment designed to remove potential criminal tendencies is at least in part a way of re-engineering people so that they suit the requirements of the system.
155. Our society tends to regard as a "sickness" any mode of thought or behavior that is inconvenient for the system, and this is plausible because when an individual doesn't fit into the system it causes pain to the individual as well as problems for the system. Thus the manipulation of an individual to adjust him to the system is seen as a "cure" for a "sickness" and therefore as good.
156. In paragraph 127 we pointed out that if the use of a new item of technology is INITIALLY optional, it does not necessarily REMAIN optional, because the new technology tends to change society in such a way that it becomes difficult or impossible for an individual to function without using that technology. This applies also to the technology of human behavior. In a world in which most children are put through a program to make them enthusiastic about studying, a parent will almost be forced to put his kid through such a program, because if he does not, then the kid will grow up to be, comparatively speaking, an ignoramus and therefore unemployable. Or suppose a biological treatment is discovered that, without undesirable side-effects, will greatly reduce the psychological stress from which so many people suffer in our society.If large numbers of people choose to undergo the treatment, then the general level of stress in society will be reduced, so that it will be possible for the system to increase the stress-producing pressures. In fact, something like this seems to have happened already with one of our society's most important psychological tools for enabling people to reduce (or at least temporarily escape from) stress, namely, mass entertainment (see paragraph 147). Our use of mass entertainment is "optional": No law requires us to watch television, listen to the radio, read magazines. Yet mass entertainment is a means of escape and stress-reduction on which most of us have become dependent. Everyone complains about the trashiness of television, but almost everyone watches it. A few have kicked the TV habit, but it would be a rare person who could get along today without using ANY form of mass entertainment. (Yet until quite recently in human history most people got along very nicely with no other entertainment than that which each local community created for itself.) Without the entertainment industry the system probably would not have been able to get away with putting as much stress-producing pressure on us as it does.
157. Assuming that industrial society survives, it is likely that technology will eventually acquire something approaching complete control over human behavior. It has been established beyond any rational doubt that human thought and behavior have a largely biological basis. As experimenters have demonstrated, feelings such as hunger, pleasure, anger and fear can be turned on and off by electrical stimulation of appropriate parts of the brain. Memories can be destroyed by damaging parts of the brain or they can be brought to the surface by electrical stimulation. Hallucinations can be induced or moods changed by drugs. There may or may not be an immaterial human soul, but if there is one it clearly is less powerful that the biological mechanisms of human behavior. For if that were not the case then researchers would not be able so easily to manipulate human feelings and behavior with drugs and electrical currents.
158. It presumably would be impractical for all people to have electrodes inserted in their heads so that they could be controlled by the authorities. But the fact that human thoughts and feelings are so open to biological intervention shows that the problem of controlling human behavior is mainly a technical problem; a problem of neurons, hormones and complex molecules; the kind of problem that is accessible to scientific attack. Given the outstanding record of our society in solving technical problems, it is overwhelmingly probable that great advances will be made in the control of human behavior.
159. Will public resistance prevent the introduction of technological control of human behavior? It certainly would if an attempt were made to introduce such control all at once. But since technological control will be introduced through a long sequence of small advances, there will be no rational and effective public resistance. (See paragraphs 127, 132, 153.)
160. To those who think that all this sounds like science fiction, we point out that yesterday's science fiction is today's fact. The Industrial Revolution has radically altered man's environment and way of life, and it is only to be expected that as technology is increasingly applied to the human body and mind, man himself will be altered as radically as his environment and way of life have been.
HUMAN RACE AT A CROSSROADS
161. But we have gotten ahead of our story. It is one thing to develop in the laboratory a series of psychological or biological techniques for manipulating human behavior and quite another to integrate these techniques into a functioning social system. The latter problem is the more difficult of the two. For example, while the techniques of educational psychology doubtless work quite well in the "lab schools" where they are developed, it is not necessarily easy to apply them effectively throughout our educational system. We all know what many of our schools are like. The teachers are too busy taking knives and guns away from the kids to subject them to the latest techniques for making them into computer nerds. Thus, in spite of all its technical advances relating to human behavior, the system to date has not been impressively successful in controlling human beings. The people whose behavior is fairly well under the control of the system are those of the type that might be called "bourgeois." But there are growing numbers of people who in one way or another are rebels against the system: welfare leaches, youth gangs, cultists, satanists, nazis, radical environmentalists, militiamen, etc.
162. The system is currently engaged in a desperate struggle to overcome certain problems that threaten its survival, among which the problems of human behavior are the most important. If the system succeeds in acquiring sufficient control over human behavior quickly enough, it will probably survive. Otherwise it will break down. We think the issue will most likely be resolved within the next several decades, say 40 to 100 years.
163. Suppose the system survives the crisis of the next several decades. By that time it will have to have solved, or at least brought under control, the principal problems that confront it, in particular that of "socializing" human beings; that is, making people sufficiently docile so that heir behavior no longer threatens the system. That being accomplished, it does not appear that there would be any further obstacle to the development of technology, and it would presumably advance toward its logical conclusion, which is complete control over everything on Earth, including human beings and all other important organisms. The system may become a unitary, monolithic organization, or it may be more or less fragmented and consist of a number of organizations coexisting in a relationship that includes elements of both cooperation and competition, just as today the government, the corporations and other large organizations both cooperate and compete with one another. Human freedom mostly will have vanished, because individuals and small groups will be impotent vis-a-vis large organizations armed with supertechnology and an arsenal of advanced psychological and biological tools for manipulating human beings, besides instruments of surveillance and physical coercion. Only a small number of people will have any real power, and even these probably will have only very limited freedom, because their behavior too will be regulated; just as today our politicians and corporation executives can retain their positions of power only as long as their behavior remains within certain fairly narrow limits.
164. Don't imagine that the systems will stop developing further techniques for controlling human beings and nature once the crisis of the next few decades is over and increasing control is no longer necessary for the system's survival. On the contrary, once the hard times are over the system will increase its control over people and nature more rapidly, because it will no longer be hampered by difficulties of the kind that it is currently experiencing. Survival is not the principal motive for extending control. As we explained in paragraphs 87-90, technicians and scientists carry on their work largely as a surrogate activity; that is, they satisfy their need for power by solving technical problems. They will continue to do this with unabated enthusiasm, and among the most interesting and challenging problems for them to solve will be those of understanding the human body and mind and intervening in their development. For the "good of humanity," of course.
165. But suppose on the other hand that the stresses of the coming decades prove to be too much for the system. If the system breaks down there may be a period of chaos, a "time of troubles" such as those that history has recorded at various epochs in the past. It is impossible to predict what would emerge from such a time of troubles, but at any rate the human race would be given a new chance. The greatest danger is that industrial society may begin to reconstitute itself within the first few years after the breakdown. Certainly there will be many people (power-hungry types especially) who will be anxious to get the factories running again.
166. Therefore two tasks confront those who hate the servitude to which the industrial system is reducing the human race. First, we must work to heighten the social stresses within the system so as to increase the likelihood that it will break down or be weakened sufficiently so that a revolution against it becomes possible. Second, it is necessary to develop and propagate an ideology that opposes technology and the industrial society if and when the system becomes sufficiently weakened. And such an ideology will help to assure that, if and when industrial society breaks down, its remnants will be smashed beyond repair, so that the system cannot be reconstituted. The factories should be destroyed, technical books burned, etc.
HUMAN SUFFERING
167. The industrial system will not break down purely as a result of revolutionary action. It will not be vulnerable to revolutionary attack unless its own internal problems of development lead it into very serious difficulties. So if the system breaks down it will do so either spontaneously, or through a process that is in part spontaneous but helped along by revolutionaries. If the breakdown is sudden, many people will die, since the world's population has become so overblown that it cannot even feed itself any longer without advanced technology. Even if the breakdown is gradual enough so that reduction of the population can occur more through lowering of the birth rate than through elevation of the death rate, the process of de-industrialization probably will be very chaotic and involve much suffering. It is naive to think it likely that technology can be phased out in a smoothly managed, orderly way, especially since the technophiles will fight stubbornly at every step. Is it therefore cruel to work for the breakdown of the system? Maybe, but maybe not. In the first place, revolutionaries will not be able to break the system down unless it is already in enough trouble so that there would be a good chance of its eventually breaking down by itself anyway; and the bigger the system grows, the more disastrous the consequences of its breakdown will be; so it may be that revolutionaries, by hastening the onset of the breakdown, will be reducing the extent of the disaster.
168. In the second place, one has to balance struggle and death against the loss of freedom and dignity. To many of us, freedom and dignity are more important than a long life or avoidance of physical pain. Besides, we all have to die some time, and it may be better to die fighting for survival, or for a cause, than to live a long but empty and purposeless life.
169. In the third place, it is not at all certain that survival of the system will lead to less suffering than breakdown of the system would. The system has already caused, and is continuing to cause, immense suffering all over the world. Ancient cultures, that for hundreds of years gave people a satisfactory relationship with each other and with their environment, have been shattered by contact with industrial society, and the result has been a whole catalogue of economic, environmental, social and psychological problems. One of the effects of the intrusion of industrial society has been that over much of the world traditional controls on population have been thrown out of balance. Hence the population explosion, with all that that implies. Then there is the psychological suffering that is widespread throughout the supposedly fortunate countries of the West (see paragraphs 44, 45). No one knows what will happen as a result of ozone depletion, the greenhouse effect and other environmental problems that cannot yet be foreseen. And, as nuclear proliferation has shown, new technology cannot be kept out of the hands of dictators and irresponsible Third World nations. Would you like to speculate about what Iraq or North Korea will do with genetic engineering?
170. "Oh!" say the technophiles, "Science is going to fix all that! We will conquer famine, eliminate psychological suffering, make everybody healthy and happy!" Yeah, sure. That's what they said 200 years ago. The Industrial Revolution was supposed to eliminate poverty, make everybody happy, etc. The actual result has been quite different. The technophiles are hopelessly naive (or self-deceiving) in their understanding of social problems. They are unaware of (or choose to ignore) the fact that when large changes, even seemingly beneficial ones, are introduced into a society, they lead to a long sequence of other changes, most of which are impossible to predict (paragraph 103). The result is disruption of the society. So it is very probable that in their attempts to end poverty and disease, engineer docile, happy personalities and so forth, the technophiles will create social systems that are terribly troubled, even more so than the present once. For example, the scientists boast that they will end famine by creating new, genetically engineered food plants. But this will allow the human population to keep expanding indefinitely, and it is well known that crowding leads to increased stress and aggression. This is merely one example of the PREDICTABLE problems that will arise. We emphasize that, as past experience has shown, technical progress will lead to other new problems that CANNOT be predicted in advance (paragraph 103). In fact, ever since the Industrial Revolution, technology has been creating new problems for society far more rapidly than it has been solving old ones. Thus it will take a long and difficult period of trial and error for the technophiles to work the bugs out of their Brave New World (if they every do). In the meantime there will be great suffering. So it is not at all clear that the survival of industrial society would involve less suffering than the breakdown of that society would. Technology has gotten the human race into a fix from which there is not likely to be any easy escape.
THE FUTURE
171. But suppose now that industrial society does survive the next several decades and that the bugs do eventually get worked out of the system, so that it functions smoothly. What kind of system will it be? We will consider several possibilities.
172. First let us postulate that the computer scientists succeed in developing intelligent machines that can do all things better than human beings can do them. In that case presumably all work will be done by vast, highly organized systems of machines and no human effort will be necessary. Either of two cases might occur. The machines might be permitted to make all of their own decisions without human oversight, or else human control over the machines might be retained.
173. If the machines are permitted to make all their own decisions, we can't make any conjectures as to the results, because it is impossible to guess how such machines might behave. We only point out that the fate of the human race would be at the mercy of the machines. It might be argued that the human race would never be foolish enough to hand over all power to the machines. But we are suggesting neither that the human race would voluntarily turn power over to the machines nor that the machines would willfully seize power. What we do suggest is that the human race might easily permit itself to drift into a position of such dependence on the machines that it would have no practical choice but to accept all of the machines' decisions. As society and the problems that face it become more and more complex and as machines become more and more intelligent, people will let machines make more and more of their decisions for them, simply because machine-made decisions will bring better results than man-made ones. Eventually a stage may be reached at which the decisions necessary to keep the system running will be so complex that human beings will be incapable of making them intelligently. At that stage the machines will be in effective control. People won't be able to just turn the machines off, because they will be so dependent on them that turning them off would amount to suicide.
174. On the other hand it is possible that human control over the machines may be retained. In that case the average man may have control over certain private machines of his own, such as his car or his personal computer, but control over large systems of machines will be in the hands of a tiny elitesjust as it is today, but with two differences. Due to improved techniques the elite will have greater control over the masses; and because human work will no longer be necessary the masses will be superfluous, a useless burden on the system. If the elite is ruthless they may simply decide to exterminate the mass of humanity. If they are humane they may use propaganda or other psychological or biological techniques to reduce the birth rate until the mass of humanity becomes extinct, leaving the world to the elite. Or, if the elite consists of soft-hearted liberals, they may decide to play the role of good shepherds to the rest of the human race. They will see to it that everyone's physical needs are satisfied, that all children are raised under psychologically hygienic conditions, that everyone has a wholesome hobby to keep him busy, and that anyone who may become dissatisfied undergoes "treatment" to cure his "problem." Of course, life will be so purposeless that people will have to be biologically or psychologically engineered either to remove their need for the power process or to make them "sublimate" their drive for power into some harmless hobby. These engineered human beings may be happy in such a society, but they most certainly will not be free. They will have been reduced to the status of domestic animals.
175. But suppose now that the computer scientists do not succeed in developing artificial intelligence, so that human work remains necessary. Even so, machines will take care of more and more of the simpler tasks so that there will be an increasing surplus of human workers at the lower levels of ability. (We see this happening already. There are many people who find it difficult or impossible to get work, because for intellectual or psychological reasons they cannot acquire the level of training necessary to make themselves useful in the present system.) On those who are employed, ever-increasing demands will be placed: They will need more and more training, more and more ability, and will have to be ever more reliable, conforming and docile, because they will be more and more like cells of a giant organism. Their tasks will be increasingly specialized, so that their work will be, in a sense, out of touch with the real world, being concentrated on one tiny slice of reality. The system will have to use any means that it can, whether psychological or biological, to engineer people to be docile, to have the abilities that the system requires and to "sublimate" their drive for power into some specialized task. But the statement that the people of such a society will have to be docile may require qualification. The society may find competitiveness useful, provided that ways are found of directing competitiveness into channels that serve the needs of the system. We can imagine a future society in which there is endless competition for positions of prestige and power. But no more than a very few people will ever reach the top, where the only real power is (see end of paragraph 163). Very repellent is a society in which a person can satisfy his need for power only by pushing large numbers of other people out of the way and depriving them of THEIR opportunity for power.
176. One can envision scenarios that incorporate aspects of more than one of the possibilities that we have just discussed. For instance, it may be that machines will take over most of the work that is of real, practical importance, but that human beings will be kept busy by being given relatively unimportant work. It has been suggested, for example, that a great development of the service industries might provide work for human beings. Thus people would spent their time shining each other's shoes, driving each other around in taxicabs, making handicrafts for one another, waiting on each other's tables, etc. This seems to us a thoroughly contemptible way for the human race to end up, and we doubt that many people would find fulfilling lives in such pointless busy-work. They would seek other, dangerous outlets (drugs, crime, "cults," hate groups) unless they were biologically or psychologically engineered to adapt them to such a way of life.
177. Needless to say, the scenarios outlined above do not exhaust all the possibilities. They only indicate the kinds of outcomes that seem to us most likely. But we can envision no plausible scenarios that are any more palatable than the ones we've just described. It is overwhelmingly probable that if the industrial-technological system survives the next 40 to 100 years, it will by that time have developed certain general characteristics: Individuals (at least those of the "bourgeois" type, who are integrated into the system and make it run, and who therefore have all the power) will be more dependent than ever on large organizations; they will be more "socialized" than ever and their physical and mental qualities to a significant extent (possibly to a very great extent) will be those that are engineered into them rather than being the results of chance (or of God's will, or whatever); and whatever may be left of wild nature will be reduced to remnants preserved for scientific study and kept under the supervision and management of scientists (hence it will no longer be truly wild). In the long run (say a few centuries from now) it is likely that neither the human race nor any other important organisms will exist as we know them today, because once you start modifying organisms through genetic engineering there is no reason to stop at any particular point, so that the modifications will probably continue until man and other organisms have been utterly transformed.
178. Whatever else may be the case, it is certain that technology is creating for human beings a new physical and social environment radically different from the spectrum of environments to which natural selection has adapted the human race physically and psychologically. If man is not adjusted to this new environment by being artificially re-engineered, then he will be adapted to it through a long and painful process of natural selection. The former is far more likely than the latter.
179. It would be better to dump the whole stinking system and take the consequences.
STRATEGY
180. The technophiles are taking us all on an utterly reckless ride into the unknown. Many people understand something of what technological progress is doing to us yet take a passive attitude toward it because they think it is inevitable. But we (FC) don't think it is inevitable. We think it can be stopped, and we will give here some indications of how to go about stopping it.
181. As we stated in paragraph 166, the two main tasks for the present are to promote social stress and instability in industrial society and to develop and propagate an ideology that opposes technology and the industrial system. When the system becomes sufficiently stressed and unstable, a revolution against technology may be possible. The pattern would be similar to that of the French and Russian Revolutions. French society and Russian society, for several decades prior to their respective revolutions, showed increasing signs of stress and weakness. Meanwhile, ideologies were being developed that offered a new world view that was quite different from the old one. In the Russian case, revolutionaries were actively working to undermine the old order. Then, when the old system was put under sufficient additional stress (by financial crisis in France, by military defeat in Russia) it was swept away by revolution. What we propose is something along the same lines.
182. It will be objected that the French and Russian Revolutions were failures. But most revolutions have two goals. One is to destroy an old form of society and the other is to set up the new form of society envisioned by the revolutionaries. The French and Russian revolutionaries failed (fortunately!) to create the new kind of society of which they dreamed, but they were quite successful in destroying the old society. We have no illusions about the feasibility of creating a new, ideal form of society. Our goal is only to destroy the existing form of society.
183. But an ideology, in order to gain enthusiastic support, must have a positive ideal as well as a negative one; it must be FOR something as well as AGAINST something. The positive ideal that we propose is Nature. That is, WILD nature: those aspects of the functioning of the Earth and its living things that are independent of human management and free of human interference and control. And with wild nature we include human nature, by which we mean those aspects of the functioning of the human individual that are not subject to regulation by organized society but are products of chance, or free will, or God (depending on your religious or philosophical opinions).
184. Nature makes a perfect counter-ideal to technology for several reasons. Nature (that which is outside the power of the system) is the opposite of technology (which seeks to expand indefinitely the power of the system). Most people will agree that nature is beautiful; certainly it has tremendous popular appeal. The radical environmentalists ALREADY hold an ideology that exalts nature and opposes technology. [30] It is not necessary for the sake of nature to set up some chimerical utopia or any new kind of social order. Nature takes care of itself: It was a spontaneous creation that existed long before any human society, and for countless centuries many different kinds of human societies coexisted with nature without doing it an excessive amount of damage. Only with the Industrial Revolution did the effect of human society on nature become really devastating. To relieve the pressure on nature it is not necessary to create a special kind of social system, it is only necessary to get rid of industrial society. Granted, this will not solve all problems. Industrial society has already done tremendous damage to nature and it will take a very long time for the scars to heal. Besides, even pre-industrial societies can do significant damage to nature. Nevertheless, getting rid of industrial society will accomplish a great deal. It will relieve the worst of the pressure on nature so that the scars can begin to heal. It will remove the capacity of organized society to keep increasing its control over nature (including human nature). Whatever kind of society may exist after the demise of the industrial system, it is certain that most people will live close to nature, because in the absence of advanced technology there is no other way that people CAN live. To feed themselves they must be peasants or herdsmen or fishermen or hunters, etc. And, generally speaking, local autonomy should tend to increase, because lack of advanced technology and rapid communications will limit the capacity of governments or other large organizations to control local communities.
185. As for the negative consequences of eliminating industrial societyswell, you can't eat your cake and have it too. To gain one thing you have to sacrifice another.
186. Most people hate psychological conflict. For this reason they avoid doing any serious thinking about difficult social issues, and they like to have such issues presented to them in simple, black-and-white terms: THIS is all good and THAT is all bad. The revolutionary ideology should therefore be developed on two levels.
187. On the more sophisticated level the ideology should address itself to people who are intelligent, thoughtful and rational. The object should be to create a core of people who will be opposed to the industrial system on a rational, thought-out basis, with full appreciation of the problems and ambiguities involved, and of the price that has to be paid for getting rid of the system. It is particularly important to attract people of this type, as they are capable people and will be instrumental in influencing others. These people should be addressed on as rational a level as possible. Facts should never intentionally be distorted and intemperate language should be avoided. This does not mean that no appeal can be made to the emotions, but in making such appeal care should be taken to avoid misrepresenting the truth or doing anything else that would destroy the intellectual respectability of the ideology.
188. On a second level, the ideology should be propagated in a simplified form that will enable the unthinking majority to see the conflict of technology vs. nature in unambiguous terms. But even on this second level the ideology should not be expressed in language that is so cheap, intemperate or irrational that it alienates people of the thoughtful and rational type. Cheap, intemperate propaganda sometimes achieves impressive short-term gains, but it will be more advantageous in the long run to keep the loyalty of a small number of intelligently committed people than to arouse the passions of an unthinking, fickle mob who will change their attitude as soon as someone comes along with a better propaganda gimmick. However, propaganda of the rabble-rousing type may be necessary when the system is nearing the point of collapse and there is a final struggle between rival ideologies to determine which will become dominant when the old world-view goes under.
189. Prior to that final struggle, the revolutionaries should not expect to have a majority of people on their side. History is made by active, determined minorities, not by the majority, which seldom has a clear and consistent idea of what it really wants. Until the time comes for the final push toward revolution [31], the task of revolutionaries will be less to win the shallow support of the majority than to build a small core of deeply committed people. As for the majority, it will be enough to make them aware of the existence of the new ideology and remind them of it frequently; though of course it will be desirable to get majority support to the extent that this can be done without weakening the core of seriously committed people.
190. Any kind of social conflict helps to destabilize the system, but one should be careful about what kind of conflict one encourages. The line of conflict should be drawn between the mass of the people and the power-holding elite of industrial society (politicians, scientists, upper-level business executives, government officials, etc.). It should NOT be drawn between the revolutionaries and the mass of the people. For example, it would be bad strategy for the revolutionaries to condemn Americans for their habits of consumption. Instead, the average American should be portrayed as a victim of the advertising and marketing industry, which has suckered him into buying a lot of junk that he doesn't need and that is very poor compensation for his lost freedom. Either approach is consistent with the facts. It is merely a matter of attitude whether you blame the advertising industry for manipulating the public or blame the public for allowing itself to be manipulated. As a matter of strategy one should generally avoid blaming the public.
191. One should think twice before encouraging any other social conflict than that between the power-holding elite (which wields technology) and the general public (over which technology exerts its power). For one thing, other conflicts tend to distract attention from the important conflicts (between power-elite and ordinary people, between technology and nature); for another thing, other conflicts may actually tend to encourage technologization, because each side in such a conflict wants to use technological power to gain advantages over its adversary. This is clearly seen in rivalries between nations. It also appears in ethnic conflicts within nations. For example, in America many black leaders are anxious to gain power for African Americans by placing back individuals in the technological power-elite. They want there to be many black government officials, sc ientists, corporation executives and so forth. In this way they are helping to absorb the African American subculture into the technological system. Generally speaking, one should encourage only those social conflicts that can be fitted into the framework of the conflicts of power-elite vs. ordinary people, technology vs nature.
192. But the way to discourage ethnic conflict is NOT through militant advocacy of minority rights (see paragraphs 21, 29). Instead, the revolutionaries should emphasize that although minorities do suffer more or less disadvantage, this disadvantage is of peripheral significance. Our real enemy is the industrial-technological system, and in the struggle against the system, ethnic distinctions are of no importance.
193. The kind of revolution we have in mind will not necessarily involve an armed uprising against any government. It may or may not involve physical violence, but it will not be a POLITICAL revolution. Its focus will be on technology and economics, not politics. [32]
194. Probably the revolutionaries should even AVOID assuming political power, whether by legal or illegal means, until the industrial system is stressed to the danger point and has proved itself to be a failure in the eyes of most people. Suppose for example that some "green" party should win control of the United States Congress in an election. In order to avoid betraying or watering down their own ideology they would have to take vigorous measures to turn economic growth into economic shrinkage. To the average man the results would appear disastrous: There would be massive unemployment, shortages of commodities, etc. Even if the grosser ill effects could be avoided through superhumanly skillful management, still people would have to begin giving up the luxuries to which they have become addicted. Dissatisfaction would grow, the "green" party would be voted out of office and the revolutionaries would have suffered a severe setback. For this reason the revolutionaries should not try to acquire political power until the system has gotten itself into such a mess that any hardships will be seen as resulting from the failures of the industrial system itself and not from the policies of the revolutionaries. The revolution against technology will probably have to be a revolution by outsiders, a revolution from below and not from above.
195. The revolution must be international and worldwide. It cannot be carried out on a nation-by-nation basis. Whenever it is suggested that the United States, for example, should cut back on technological progress or economic growth, people get hysterical and start screaming that if we fall behind in technology the Japanese will get ahead of us. Holy robots! The world will fly off its orbit if the Japanese ever sell more cars than we do! (Nationalism is a great promoter of technology.) More reasonably, it is argued that if the relatively democratic nations of the world fall behind in technology while nasty, dictatorial nations like China, Vietnam and North Korea continue to progress, eventually the dictators may come to dominate the world. That is why the industrial system should be attacked in all nations simultaneously, to the extent that this may be possible. True, there is no assurance that the industrial system can be destroyed at approximately the same time all over the world, and it is even conceivable that the attempt to overthrow the system could lead instead to the domination of the system by dictators. That is a risk that has to be taken. And it is worth taking, since the difference between a "democratic" industrial system and one controlled by dictators is small compared with the difference between an industrial system and a non-industrial one. [33] It might even be argued that an industrial system controlled by dictators would be preferable, because dictator-controlled systems usually have proved inefficient, hence they are presumably more likely to break down. Look at Cuba.
196. Revolutionaries might consider favoring measures that tend to bind the world economy into a unified whole. Free trade agreements like NAFTA and GATT are probably harmful to the environment in the short run, but in the long run they may perhaps be advantageous because they foster economic interdependence between nations. It will be easier to destroy the industrial system on a worldwide basis if the world economy is so unified that its breakdown in any one major nation will lead to its breakdown in all industrialized nations.
197. Some people take the line that modern man has too much power, too much control over nature; they argue for a more passive attitude on the part of the human race. At best these people are expressing themselves unclearly, because they fail to distinguish between power for LARGE ORGANIZATIONS and power for INDIVIDUALS and SMALL GROUPS. It is a mistake to argue for powerlessness and passivity, because people NEED power. Modern man as a collective entitysthat is, the industrial systemshas immense power over nature, and we (FC) regard this as evil. But modern INDIVIDUALS and SMALL GROUPS OF INDIVIDUALS have far less power than primitive man ever did. Generally speaking, the vast power of "modern man" over nature is exercised not by individuals or small groups but by large organizations. To the extent that the average modern INDIVIDUAL can wield the power of technology, he is permitted to do so only within narrow limits and only under the supervision and control of the system. (You need a license for everything and with the license come rules and regulations.) The individual has only those technological powers with which the system chooses to provide him. His PERSONAL power over nature is slight.
198. Primitive INDIVIDUALS and SMALL GROUPS actually had considerable power over nature; or maybe it would be better to say power WITHIN nature. When primitive man needed food he knew how to find and prepare edible roots, how to track game and take it with homemade weapons. He knew how to protect himself from heat, cold, rain, dangerous animals, etc. But primitive man did relatively little damage to nature because the COLLECTIVE power of primitive society was negligible compared to the COLLECTIVE power of industrial society.
199. Instead of arguing for powerlessness and passivity, one should argue that the power of the INDUSTRIAL SYSTEM should be broken, and that this will greatly INCREASE the power and freedom of INDIVIDUALS and SMALL GROUPS.
200. Until the industrial system has been thoroughly wrecked, the destruction of that system must be the revolutionaries' ONLY goal. Other goals would distract attention and energy from the main goal. More importantly, if the revolutionaries permit themselves to have any other goal than the destruction of technology, they will be tempted to use technology as a tool for reaching that other goal. If they give in to that temptation, they will fall right back into the technological trap, because modern technology is a unified, tightly organized system, so that, in order to retain SOME technology, one finds oneself obliged to retain MOST technology, hence one ends up sacrificing only token amounts of technology.
201. Suppose for example that the revolutionaries took "social justice" as a goal. Human nature being what it is, social justice would not come about spontaneously; it would have to be enforced. In order to enforce it the revolutionaries would have to retain central organization and control. For that they would need rapid long-distance transportation and communication, and therefore all the technology needed to support the transportation and communication systems. To feed and clothe poor people they would have to use agricultural and manufacturing technology. And so forth. So that the attempt to insure social justice would force them to retain most parts of the technological system. Not that we have anything against social justice, but it must not be allowed to interfere with the effort to get rid of the technological system.
202. It would be hopeless for revolutionaries to try to attack the system without using SOME modern technology. If nothing else they must use the communications media to spread their message. But they should use modern technology for only ONE purpose: to attack the technological system.
203. Imagine an alcoholic sitting with a barrel of wine in front of him. Suppose he starts saying to himself, "Wine isn't bad for you if used in moderation. Why, they say small amounts of wine are even good for you! It won't do me any harm if I take just one little drink.... " Well you know what is going to happen. Never forget that the human race with technology is just like an alcoholic with a barrel of wine.
204. Revolutionaries should have as many children as they can. There is strong scientific evidence that social attitudes are to a significant extent inherited. No one suggests that a social attitude is a direct outcome of a person's genetic constitution, but it appears that personality traits are partly inherited and that certain personality traits tend, within the context of our society, to make a person more likely to hold this or that social attitude. Objections to these findings have been raised, but the objections are feeble and seem to be ideologically motivated. In any event, no one denies that children tend on the average to hold social attitudes similar to those of their parents. From our point of view it doesn't matter all that much whether the attitudes are passed on genetically or through childhood training. In either case they ARE passed on.
205. The trouble is that many of the people who are inclined to rebel against the industrial system are also concerned about the population problems, hence they are apt to have few or no children. In this way they may be handing the world over to the sort of people who support or at least accept the industrial system. To insure the strength of the next generation of revolutionaries the present generation should reproduce itself abundantly. In doing so they will be worsening the population problem only slightly. And the important problem is to get rid of the industrial system, because once the industrial system is gone the world's population necessarily will decrease (see paragraph 167); whereas, if the industrial system survives, it will continue developing new techniques of food production that may enable the world's population to keep increasing almost indefinitely.
206. With regard to revolutionary strategy, the only points on which we absolutely insist are that the single overriding goal must be the elimination of modern technology, and that no other goal can be allowed to compete with this one. For the rest, revolutionaries should take an empirical approach. If experience indicates that some of the recommendations made in the foregoing paragraphs are not going to give good results, then those recommendations should be discarded.
TWO KINDS OF TECHNOLOGY
207. An argument likely to be raised against our proposed revolution is that it is bound to fail, because (it is claimed) throughout history technology has always progressed, never regressed, hence technological regression is impossible. But this claim is false.
208. We distinguish between two kinds of technology, which we will call small-scale technology and organization-dependent technology. Small-scale technology is technology that can be used by small-scale communities without outside assistance. Organization-dependent technology is technology that depends on large-scale social organization. We are aware of no significant cases of regression in small-scale technology. But organization-dependent technology DOES regress when the social organization on which it depends breaks down. Example: When the Roman Empire fell apart the Romans' small-scale technology survived because any clever village craftsman could build, for instance, a water wheel, any skilled smith could make steel by Roman methods, and so forth. But the Romans' organization-dependent technology DID regress. Their aqueducts fell into disrepair and were never rebuilt. Their techniques of road construction were lost. The Roman system of urban sanitation was forgotten, so that not until r ather recent times did the sanitation of European cities equal that of Ancient Rome.
209. The reason why technology has seemed always to progress is that, until perhaps a century or two before the Industrial Revolution, most technology was small-scale technology. But most of the technology developed since the Industrial Revolution is organization-dependent technology. Take the refrigerator for example. Without factory-made parts or the facilities of a post-industrial machine shop it would be virtually impossible for a handful of local craftsmen to build a refrigerator. If by some miracle they did succeed in building one it would be useless to them without a reliable source of electric power. So they would have to dam a stream and build a generator. Generators require large amounts of copper wire. Imagine trying to make that wire without modern machinery. And where would they get a gas suitable for refrigeration? It would be much easier to build an icehouse or preserve food by drying or picking, as was done before the invention of the refrigerator.
210. So it is clear that if the industrial system were once thoroughly broken down, refrigeration technology would quickly be lost. The same is true of other organization-dependent technology. And once this technology had been lost for a generation or so it would take centuries to rebuild it, just as it took centuries to build it the first time around. Surviving technical books would be few and scattered. An industrial society, if built from scratch without outside help, can only be built in a series of stages: You need tools to make tools to make tools to make tools ... . A long process of economic development and progress in social organization is required. And, even in the absence of an ideology opposed to technology, there is no reason to believe that anyone would be interested in rebuilding industrial society. The enthusiasm for "progress" is a phenomenon peculiar to the modern form of society, and it seems not to have existed prior to the 17th century or thereabouts.
211. In the late Middle Ages there were four main civilizations that were about equally "advanced": Europe, the Islamic world, India, and the Far East (China, Japan, Korea). Three of those civilizations remained more or less stable, and only Europe became dynamic. No one knows why Europe became dynamic at that time; historians have their theories but these are only speculation. At any rate, it is clear that rapid development toward a technological form of society occurs only under special conditions. So there is no reason to assume that a long-lasting technological regression cannot be brought about.
212. Would society EVENTUALLY develop again toward an industrial-technological form? Maybe, but there is no use in worrying about it, since we can't predict or control events 500 or 1,000 years in the future. Those problems must be dealt with by the people who will live at that time.
THE DANGER OF LEFTISM
213. Because of their need for rebellion and for membership in a movement, leftists or persons of similar psychological type often are unattracted to a rebellious or activist movement whose goals and membership are not initially leftist. The resulting influx of leftish types can easily turn a non-leftist movement into a leftist one, so that leftist goals replace or distort the original goals of the movement.
214. To avoid this, a movement that exalts nature and opposes technology must take a resolutely anti-leftist stance and must avoid all collaboration with leftists. Leftism is in the long run inconsistent with wild nature, with human freedom and with the elimination of modern technology. Leftism is collectivist; it seeks to bind together the entire world (both nature and the human race) into a unified whole. But this implies management of nature and of human life by organized society, and it requires advanced technology. You can't have a united world without rapid transportation and communication, you can't make all people love one another without sophisticated psychological techniques, you can't have a "planned society" without the necessary technological base. Above all, leftism is driven by the need for power, and the leftist seeks power on a collective basis, through identification with a mass movement or an organization. Leftism is unlikely ever to give up technology, because technology is too valuable a source of collective power.
215. The anarchist [34] too seeks power, but he seeks it on an individual or small-group basis; he wants individuals and small groups to be able to control the circumstances of their own lives. He opposes technology because it makes small groups dependent on large organizations.
216. Some leftists may seem to oppose technology, but they will oppose it only so long as they are outsiders and the technological system is controlled by non-leftists. If leftism ever becomes dominant in society, so that the technological system becomes a tool in the hands of leftists, they will enthusiastically use it and promote its growth. In doing this they will be repeating a pattern that leftism has shown again and again in the past. When the Bolsheviks in Russia were outsiders, they vigorously opposed censorship and the secret police, they advocated self-determination for ethnic minorities, and so forth; but as soon as they came into power themselves, they imposed a tighter censorship and created a more ruthless secret police than any that had existed under the tsars, and they oppressed ethnic minorities at least as much as the tsars had done. In the United States, a couple of decades ago when leftists were a minority in our universities, leftist professors were vigorous proponents of academic freedom, but today, in those of our universities where leftists have become dominant, they have shown themselves ready to take away from everyone else's academic freedom. (This is "political correctness.") The same will happen with leftists and technology: They will use it to oppress everyone else if they ever get it under their own control.
217. In earlier revolutions, leftists of the most power-hungry type, repeatedly, have first cooperated with non-leftist revolutionaries, as well as with leftists of a more libertarian inclination, and later have double-crossed them to seize power for themselves. Robespierre did this in the French Revolution, the Bolsheviks did it in the Russian Revolution, the communists did it in Spain in 1938 and Castro and his followers did it in Cuba. Given the past history of leftism, it would be utterly foolish for non-leftist revolutionaries today to collaborate with leftists.
218. Various thinkers have pointed out that leftism is a kind of religion. Leftism is not a religion in the strict sense because leftist doctrine does not postulate the existence of any supernatural being. But, for the leftist, leftism plays a psychological role much like that which religion plays for some people. The leftist NEEDS to believe in leftism; it plays a vital role in his psychological economy. His beliefs are not easily modified by logic or facts. He has a deep conviction that leftism is morally Right with a capital R, and that he has not only a right but a duty to impose leftist morality on everyone. (However, many of the people we are referring to as "leftists" do not think of themselves as leftists and would not describe their system of beliefs as leftism. We use the term "leftism" because we don't know of any better words to designate the spectrum of related creeds that includes the feminist, gay rights, political correctness, etc., movements, and because these movements have a strong affinity with the old left. See paragraphs 227-230.)
219. Leftism is a totalitarian force. Wherever leftism is in a position of power it tends to invade every private corner and force every thought into a leftist mold. In part this is because of the quasi-religious character of leftism; everything contrary to leftist beliefs represents Sin. More importantly, leftism is a totalitarian force because of the leftists' drive for power. The leftist seeks to satisfy his need for power through identification with a social movement and he tries to go through the power process by helping to pursue and attain the goals of the movement (see paragraph 83). But no matter how far the movement has gone in attaining its goals the leftist is never satisfied, because his activism is a surrogate activity (see paragraph 41). That is, the leftist's real motive is not to attain the ostensible goals of leftism; in reality he is motivated by the sense of power he gets from struggling for and then reaching a social goal. [35] Consequently the leftist is never satisfied with the goals he has already attained; his need for the power process leads him always to pursue some new goal. The leftist wants equal opportunities for minorities. When that is attained he insists on statistical equality of achievement by minorities. And as long as anyone harbors in some corner of his mind a negative attitude toward some minority, the leftist has to re-educated him. And ethnic minorities are not enough; no one can be allowed to have a negative attitude toward homosexuals, disabled people, fat people, old people, ugly people, and on and on and on. It's not enough that the public should be informed about the hazards of smoking; a warning has to be stamped on every package of cigarettes. Then cigarette advertising has to be restricted if not banned. The activists will never be satisfied until tobacco is outlawed, and after that it will be alcohol, then junk food, etc. Activists have fought gross child abuse, which is reasonable. But now they want to stop all spanking. When they have done that they will want to ban something else they consider unwholesome, then another thing and then another. They will never be satisfied until they have complete control over all child rearing practices. And then they will move on to another cause.
220. Suppose you asked leftists to make a list of ALL the things that were wrong with society, and then suppose you instituted EVERY social change that they demanded. It is safe to say that within a couple of years the majority of leftists would find something new to complain about, some new social "evil" to correct because, once again, the leftist is motivated less by distress at society's ills than by the need to satisfy his drive for power by imposing his solutions on society.
221. Because of the restrictions placed on their thoughts and behavior by their high level of socialization, many leftists of the over-socialized type cannot pursue power in the ways that other people do. For them the drive for power has only one morally acceptable outlet, and that is in the struggle to impose their morality on everyone.
222. Leftists, especially those of the oversocialized type, are True Believers in the sense of Eric Hoffer's book, "The True Believer." But not all True Believers are of the same psychological type as leftists. Presumably a true-believing nazi, for instance, is very different psychologically from a true-believing leftist. Because of their capacity for single-minded devotion to a cause, True Believers are a useful, perhaps a necessary, ingredient of any revolutionary movement. This presents a problem with which we must admit we don't know how to deal. We aren't sure how to harness the energies of the True Believer to a revolution against technology. At present all we can say is that no True Believer will make a safe recruit to the revolution unless his commitment is exclusively to the destruction of technology. If he is committed also to another ideal, he may want to use technology as a tool for pursuing that other ideal (see paragraphs 220, 221).
223. Some readers may say, "This stuff about leftism is a lot of crap. I know John and Jane who are leftish types and they don't have all these totalitarian tendencies." It's quite true that many leftists, possibly even a numerical majority, are decent people who sincerely believe in tolerating others' values (up to a point) and wouldn't want to use high-handed methods to reach their social goals. Our remarks about leftism are not meant to apply to every individual leftist but to describe the general character of leftism as a movement. And the general character of a movement is not necessarily determined by the numerical proportions of the various kinds of people involved in the movement.
224. The people who rise to positions of power in leftist movements tend to be leftists of the most power-hungry type, because power-hungry people are those who strive hardest to get into positions of power. Once the power-hungry types have captured control of the movement, there are many leftists of a gentler breed who inwardly disapprove of many of the actions of the leaders, but cannot bring themselves to oppose them. They NEED their faith in the movement, and because they cannot give up this faith they go along with the leaders. True, SOME leftists do have the guts to oppose the totalitarian tendencies that emerge, but they generally lose, because the power-hungry types are better organized, are more ruthless and Machiavellian and have taken care to build themselves a strong power base.
225. These phenomena appeared clearly in Russia and other countries that were taken over by leftists. Similarly, before the breakdown of communism in the USSR, leftish types in the West would seldom criticize that country. If prodded they would admit that the USSR did many wrong things, but then they would try to find excuses for the communists and begin talking about the faults of the West. They always opposed Western military resistance to communist aggression. Leftish types all over the world vigorously protested the U.S. military action in Vietnam, but when the USSR invaded Afghanistan they did nothing. Not that they approved of the Soviet actions; but because of their leftist faith, they just couldn't bear to put themselves in opposition to communism. Today, in those of our universities where "political correctness" has become dominant, there are probably many leftish types who privately disapprove of the suppression of academic freedom, but they go along with it anyway.
226. Thus the fact that many individual leftists are personally mild and fairly tolerant people by no means prevents leftism as a whole form having a totalitarian tendency.
227. Our discussion of leftism has a serious weakness. It is still far from clear what we mean by the word "leftist." There doesn't seem to be much we can do about this. Today leftism is fragmented into a whole spectrum of activist movements. Yet not all activist movements are leftist, and some activist movements (e.g., radical environmentalism) seem to include both personalities of the leftist type and personalities of thoroughly un-leftist types who ought to know better than to collaborate with leftists. Varieties of leftists fade out gradually into varieties of non-leftists and we ourselves would often be hard-pressed to decide whether a given individual is or is not a leftist. To the extent that it is defined at all, our conception of leftism is defined by the discussion of it that we have given in this article, and we can only advise the reader to use his own judgment in deciding who is a leftist.
228. But it will be helpful to list some criteria for diagnosing leftism. These criteria cannot be applied in a cut and dried manner. Some individuals may meet some of the criteria without being leftists, some leftists may not meet any of the criteria. Again, you just have to use your judgment.
229. The leftist is oriented toward large-scale collectivism. He emphasizes the duty of the individual to serve society and the duty of society to take care of the individual. He has a negative attitude toward individualism. He often takes a moralistic tone. He tends to be for gun control, for sex education and other psychologically "enlightened" educational methods, for social planning, for affirmative action, for multiculturalism. He tends to identify with victims. He tends to be against competition and against violence, but he often finds excuses for those leftists who do commit violence. He is fond of using the common catch-phrases of the left, like "racism," "sexism," "homophobia," "capitalism," "imperialism," "neocolonialism," "genocide," "social change," "social justice," "social responsibility." Maybe the best diagnostic trait of the leftist is his tendency to sympathize with the following movements: feminism, gay rights, ethnic rights, disability rights, animal rights, political correctness. Anyone who strongly sympathizes with ALL of these movements is almost certainly a leftist. [36]
230. The more dangerous leftists, that is, those who are most power-hungry, are often characterized by arrogance or by a dogmatic approach to ideology. However, the most dangerous leftists of all may be certain oversocialized types who avoid irritating displays of aggressiveness and refrain from advertising their leftism, but work quietly and unobtrusively to promote collectivist values, "enlightened" psychological techniques for socializing children, dependence of the individual on the system, and so forth. These crypto-leftists (as we may call them) approximate certain bourgeois types as far as practical action is concerned, but differ from them in psychology, ideology and motivation. The ordinary bourgeois tries to bring people under control of the system in order to protect his way of life, or he does so simply because his attitudes are conventional. The crypto-leftist tries to bring people under control of the system because he is a True Believer in a collectivistic ideology. The crypto-leftist is differentiated from the average leftist of the oversocialized type by the fact that his rebellious impulse is weaker and he is more securely socialized. He is differentiated from the ordinary well-socialized bourgeois by the fact that there is some deep lack within him that makes it necessary for him to devote himself to a cause and immerse himself in a collectivity. And maybe his (well-sublimated) drive for power is stronger than that of the average bourgeois.
FINAL NOTE
231. Throughout this article we've made imprecise statements and statements that ought to have had all sorts of qualifications and reservations attached to them; and some of our statements may be flatly false. Lack of sufficient information and the need for brevity made it impossible for us to formulate our assertions more precisely or add all the necessary qualifications. And of course in a discussion of this kind one must rely heavily on intuitive judgment, and that can sometimes be wrong. So we don't claim that this article expresses more than a crude approximation to the truth.
232. All the same, we are reasonably confident that the general outlines of the picture we have painted here are roughly correct. Just one possible weak point needs to be mentioned. We have portrayed leftism in its modern form as a phenomenon peculiar to our time and as a symptom of the disruption of the power process. But we might possibly be wrong about this. Oversocialized types who try to satisfy their drive for power by imposing their morality on everyone have certainly been around for a long time. But we THINK that the decisive role played by feelings of inferiority, low self-esteem, powerlessness, identification with victims by people who are not themselves victims, is a peculiarity of modern leftism. Identification with victims by people not themselves victims can be seen to some extent in 19th century leftism and early Christianity but as far as we can make out, symptoms of low self-esteem, etc., were not nearly so evident in these movements, or in any other movements, as they are in modern leftism. But we are not in a position to assert confidently that no such movements have existed prior to modern leftism. This is a significant question to which historians ought to give their attention.
Notes
1. (Paragraph 19) We are asserting that ALL, or even most, bullies and ruthless competitors suffer from feelings of inferiority.
2. (Paragraph 25) During the Victorian period many oversocialized people suffered from serious psychological problems as a result of repressing or trying to repress their sexual feelings. Freud apparently based his theories on people of this type. Today the focus of socialization has shifted from sex to aggression.
3. (Paragraph 27) Not necessarily including specialists in engineering or the "hard" sciences.
4. (Paragraph 28) There are many individuals of the middle and upper classes who resist some of these values, but usually their resistance is more or less covert. Such resistance appears in the mass media only to a very limited extent. The main thrust of propaganda in our society is in favor of the stated values.
The main reason why these values have become, so to speak, the official values of our society is that they are useful to the industrial system. Violence is discouraged because it disrupts the functioning of the system. Racism is discouraged because ethnic conflicts also disrupt the system, and discrimination wastes the talents of minority-group members who could be useful to the system. Poverty must be "cured" because the underclass causes problems for the system and contact with the underclass lowers the morale of the other classes. Women are encouraged to have careers because their talents are useful to the system and, more importantly, because by having regular jobs women become better integrated into the system and tied directly to it rather than to their families. This helps to weaken family solidarity. (The leaders of the system say they want to strengthen the family, but they really mean is that they want the family to serve as an effective tool for socializing children in accord with the needs of the system. We argue in paragraphs 51, 52 that the system cannot afford to let the family or other small-scale social groups be strong or autonomous.)
5. (Paragraph 42) It may be argued that the majority of people don't want to make their own decisions but want leaders to do their thinking for them. There is an element of truth in this. People like to make their own decisions in small matters, but making decisions on difficult, fundamental questions requires facing up to psychological conflict, and most people hate psychological conflict. Hence they tend to lean on others in making difficult decisions. But it does not follow that they like to have decisions imposed upon them without having any opportunity to influence those decisions. The majority of people are natural followers, not leaders, but they like to have direct personal access to their leaders, they want to be able to influence the leaders and participate to some extent in making even the difficult decisions. At least to that degree they need autonomy.
6. (Paragraph 44) Some of the symptoms listed are similar to those shown by caged animals.
To explain how these symptoms arise from deprivation with respect to the power process:
Common-sense understanding of human nature tells one that lack of goals whose attainment requires effort leads to boredom and that boredom, long continued, often leads eventually to depression. Failure to attain goals leads to frustration and lowering of self-esteem. Frustration leads to anger, anger to aggression, often in the form of spouse or child abuse. It has been shown that long-continued frustration commonly leads to depression and that depression tends to cause guilt, sleep disorders, eating disorders and bad feelings about oneself. Those who are tending toward depression seek pleasure as an antidote; hence insatiable hedonism and excessive sex, with perversions as a means of getting new kicks. Boredom too tends to cause excessive pleasure-seeking since, lacking other goals, people often use pleasure as a goal. See accompanying diagram.
The foregoing is a simplification. Reality is more complex, and of course, deprivation with respect to the power process is not the ONLY cause of the symptoms described.
By the way, when we mention depression we do not necessarily mean depression that is severe enough to be treated by a psychiatrist. Often only mild forms of depression are involved. And when we speak of goals we do not necessarily mean long-term, thought-out goals. For many or most people through much of human history, the goals of a hand-to-mouth existence (merely providing oneself and one's family with food from day to day) have been quite sufficient.
7. (Paragraph 52) A partial exception may be made for a few passive, inward-looking groups, such as the Amish, which have little effect on the wider society. Apart from these, some genuine small-scale communities do exist in America today. For instance, youth gangs and "cults." Everyone regards them as dangerous, and so they are, because the members of these groups are loyal primarily to one another rather than to the system, hence the system cannot control them.
Or take the gypsies. The gypsies commonly get away with theft and fraud because their loyalties are such that they can always get other gypsies to give testimony that "proves" their innocence. Obviously the system would be in serious trouble if too many people belonged to such groups.
Some of the early-20th century Chinese thinkers who were concerned with modernizing China recognized the necessity breaking down small-scale social groups such as the family: "(According to Sun Yat-sen) the Chinese people needed a new surge of patriotism, which would lead to a transfer of loyalty from the family to the state.... (According to Li Huang) traditional attachments, particularly to the family had to be abandoned if nationalism were to develop in China." (Chester C. Tan, "Chinese Political Thought in the Twentieth Century," page 125, page 297.)
8. (Paragraph 56) Yes, we know that 19th century America had its problems, and serious ones, but for the sake of brevity we have to express ourselves in simplified terms.
9. (Paragraph 61) We leave aside the "underclass." We are speaking of the mainstream.
10. (Paragraph 62) Some social scientists, educators, "mental health" professionals and the like are doing their best to push the social drives into group 1 by trying to see to it that everyone has a satisfactory social life.
11. (Paragraphs 63, 82) Is the drive for endless material acquisition really an artificial creation of the advertising and marketing industry? Certainly there is no innate human drive for material acquisition. There have been many cultures in which people have desired little material wealth beyond what was necessary to satisfy their basic physical needs (Australian aborigines, traditional Mexican peasant culture, some African cultures). On the other hand there have also been many pre-industrial cultures in which material acquisition has played an important role. So we can't claim that today's acquisition-oriented culture is exclusively a creation of the advertising and marketing industry. But it is clear that the advertising and marketing industry has had an important part in creating that culture. The big corporations that spend millions on advertising wouldn't be spending that kind of money without solid proof that they were getting it back in increased sales. One member of FC met a sales manager a couple of years ago who was frank enough to tell him, "Our job is to make people buy things they don't want and don't need." He then described how an untrained novice could present people with the facts about a product, and make no sales at all, while a trained and experienced professional salesman would make lots of sales to the same people. This shows that people are manipulated into buying things they don't really want.
12. (Paragraph 64) The problem of purposelessness seems to have become less serious during the last 15 years or so, because people now feel less secure physically and economically than they did earlier, and the need for security provides them with a goal. But purposelessness has been replaced by frustration over the difficulty of attaining security. We emphasize the problem of purposelessness because the liberals and leftists would wish to solve our social problems by having society guarantee everyone's security; but if that could be done it would only bring back the problem of purposelessness. The real issue is not whether society provides well or poorly for people's security; the trouble is that people are dependent on the system for their security rather than having it in their own hands. This, by the way, is part of the reason why some people get worked up about the right to bear arms; possession of a gun puts that aspect of their security in their own hands.
13. (Paragraph 66) Conservatives' efforts to decrease the amount of government regulation are of little benefit to the average man. For one thing, only a fraction of the regulations can be eliminated because most regulations are necessary. For another thing, most of the deregulation affects business rather than the average individual, so that its main effect is to take power from the government and give it to private corporations. What this means for the average man is that government interference in his life is replaced by interference from big corporations, which may be permitted, for example, to dump more chemicals that get into his water supply and give him cancer. The conservatives are just taking the average man for a sucker, exploiting his resentment of Big Government to promote the power of Big Business.
14. (Paragraph 73) When someone approves of the purpose for which propaganda is being used in a given case, he generally calls it "education" or applies to it some similar euphemism. But propaganda is propaganda regardless of the purpose for which it is used.
15. (Paragraph 83) We are not expressing approval or disapproval of the Panama invasion. We only use it to illustrate a point.
16. (Paragraph 95) When the American colonies were under British rule there were fewer and less effective legal guarantees of freedom than there were after the American Constitution went into effect, yet there was more personal freedom in pre-industrial America, both before and after the War of Independence, than there was after the Industrial Revolution took hold in this country. We quote from "Violence in America: Historical and Comparative Perspectives," edited by Hugh Davis Graham and Ted Robert Gurr, Chapter 12 by Roger Lane, pages 476-478:
"The progressive heightening of standards of propriety, and with it the increasing reliance on official law enforcement (in 19th century America) ... were common to the whole society.... [T]he change in social behavior is so long term and so widespread as to suggest a connection with the most fundamental of contemporary social processes; that of industrial urbanization itself...."Massachusetts in 1835 had a population of some 660,940, 81 percent rural, overwhelmingly preindustrial and native born. It's citizens were used to considerable personal freedom. Whether teamsters, farmers or artisans, they were all accustomed to setting their own schedules, and the nature of their work made them physically independent of each other.... Individual problems, sins or even crimes, were not generally cause for wider social concern...."But the impact of the twin movements to the city and to the factory, both just gathering force in 1835, had a progressive effect on personal behavior throughout the 19th century and into the 20th. The factory demanded regularity of behavior, a life governed by obedience to the rhythms of clock and calendar, the demands of foreman and supervisor. In the city or town, the needs of living in closely packed neighborhoods inhibited many actions previously unobjectionable. Both blue- and white-collar employees in larger establishments were mutually dependent on their fellows; as one man's work fit into anther's, so one man's business was no longer his own.
"The results of the new organization of life and work were apparent by 1900, when some 76 percent of the 2,805,346 inhabitants of Massachusetts were classified as urbanites. Much violent or irregular behavior which had been tolerable in a casual, independent society was no longer acceptable in the more formalized, cooperative atmosphere of the later period.... The move to the cities had, in short, produced a more tractable, more socialized, more 'civilized' generation than its predecessors."
17. (Paragraph 117) Apologists for the system are fond of citing cases in which elections have been decided by one or two votes, but such cases are rare.
18. (Paragraph 119) "Today, in technologically advanced lands, men live very similar lives in spite of geographical, religious, and political differences. The daily lives of a Christian bank clerk in Chicago, a Buddhist bank clerk in Tokyo, and a Communist bank clerk in Moscow are far more alike than the life of any one of them is like that of any single man who lived a thousand years ago. These similarities are the result of a common technology...." L. Sprague de Camp, "The Ancient Engineers," Ballantine edition, page 17.
The lives of the three bank clerks are not IDENTICAL. Ideology does have SOME effect. But all technological societies, in order to survive, must evolve along APPROXIMATELY the same trajectory.
19. (Paragraph 123) Just think an irresponsible genetic engineer might create a lot of terrorists.
20. (Paragraph 124) For a further example of undesirable consequences of medical progress, suppose a reliable cure for cancer is discovered. Even if the treatment is too expensive to be available to any but the elite, it will greatly reduce their incentive to stop the escape of carcinogens into the environment.
21. (Paragraph 128) Since many people may find paradoxical the notion that a large number of good things can add up to a bad thing, we illustrate with an analogy. Suppose Mr. A is playing chess with Mr. B. Mr. C, a Grand Master, is looking over Mr. A's shoulder. Mr. A of course wants to win his game, so if Mr. C points out a good move for him to make, he is doing Mr. A a favor. But suppose now that Mr. C tells Mr. A how to make ALL of his moves. In each particular instance he does Mr. A a favor by showing him his best move, but by making ALL of his moves for him he spoils his game, since there is not point in Mr. A's playing the game at all if someone else makes all his moves.
The situation of modern man is analogous to that of Mr. A. The system makes an individual's life easier for him in innumerable ways, but in doing so it deprives him of control over his own fate.
22. (Paragraph 137) Here we are considering only the conflict of values within the mainstream. For the sake of simplicity we leave out of the picture "outsider" values like the idea that wild nature is more important than human economic welfare.
23. (Paragraph 137) Self-interest is not necessarily MATERIAL self-interest. It can consist in fulfillment of some psychological need, for example, by promoting one's own ideology or religion.
24. (Paragraph 139) A qualification: It is in the interest of the system to permit a certain prescribed degree of freedom in some areas. For example, economic freedom (with suitable limitations and restraints) has proved effective in promoting economic growth. But only planned, circumscribed, limited freedom is in the interest of the system. The individual must always be kept on a leash, even if the leash is sometimes long (see paragraphs 94, 97).
25. (Paragraph 143) We don't mean to suggest that the efficiency or the potential for survival of a society has always been inversely proportional to the amount of pressure or discomfort to which the society subjects people. That certainly is not the case. There is good reason to believe that many primitive societies subjected people to less pressure than European society did, but European society proved far more efficient than any primitive society and always won out in conflicts with such societies because of the advantages conferred by technology.
26. (Paragraph 147) If you think that more effective law enforcement is unequivocally good because it suppresses crime, then remember that crime as defined by the system is not necessarily what YOU would call crime. Today, smoking marijuana is a "crime," and, in some places in the U.S., so is possession of an unregistered handgun. Tomorrow, possession of ANY firearm, registered or not, may be made a crime, and the same thing may happen with disapproved methods of child-rearing, such as spanking. In some countries, expression of dissident political opinions is a crime, and there is no certainty that this will never happen in the U.S., since no constitution or political system lasts forever.
If a society needs a large, powerful law enforcement establishment, then there is something gravely wrong with that society; it must be subjecting people to severe pressures if so many refuse to follow the rules, or follow them only because forced. Many societies in the past have gotten by with little or no formal law-enforcement.
27. (Paragraph 151) To be sure, past societies have had means of influencing human behavior, but these have been primitive and of low effectiveness compared with the technological means that are now being developed.
28. (Paragraph 152) However, some psychologists have publicly expressed opinions indicating their contempt for human freedom. And the mathematician Claude Shannon was quoted in Omni (August 1987) as saying, "I visualize a time when we will be to robots what dogs are to humans, and I'm rooting for the machines."
29. (Paragraph 154) This is no science fiction! After writing paragraph 154 we came across an article in Scientific American according to which scientists are actively developing techniques for identifying possible future criminals and for treating them by a combination of biological and psychological means. Some scientists advocate compulsory application of the treatment, which may be available in the near future. (See "Seeking the Criminal Element," by W. Wayt Gibbs, Scientific American, March 1995.) Maybe you think this is OK because the treatment would be applied to those who might become violent criminals. But of course it won't stop there. Next, a treatment will be applied to those who might become drunk drivers (they endanger human life too), then perhaps to peel who spank their children, then to environmentalists who sabotage logging equipment, eventually to anyone whose behavior is inconvenient for the system.
30. (Paragraph 184) A further advantage of nature as a counter-ideal to technology is that, in many people, nature inspires the kind of reverence that is associated with religion, so that nature could perhaps be idealized on a religious basis. It is true that in many societies religion has served as a support and justification for the established order, but it is also true that religion has often provided a basis for rebellion. Thus it may be useful to introduce a religious element into the rebellion against technology, the more so because Western society today has no strong religious foundation. Religion, nowadays either is used as cheap and transparent support for narrow, short-sighted selfishness (some conservatives use it this way), or even is cynically exploited to make easy money (by many evangelists), or has degenerated into crude irrationalism (fundamentalist protestant sects, "cults"), or is simply stagnant (Catholicism, main-line Protestantism). The nearest thing to a strong, widespread, dynamic religion that the West has seen in recent times has been the quasi-religion of leftism, but leftism today is fragmented and has no clear, unified, inspiring goal.
Thus there is a religious vacuum in our society that could perhaps be filled by a religion focused on nature in opposition to technology. But it would be a mistake to try to concoct artificially a religion to fill this role. Such an invented religion would probably be a failure. Take the "Gaia" religion for example. Do its adherents REALLY believe in it or are they just play-acting? If they are just play-acting their religion will be a flop in the end.
It is probably best not to try to introduce religion into the conflict of nature vs. technology unless you REALLY believe in that religion yourself and find that it arouses a deep, strong, genuine response in many other people.
31. (Paragraph 189) Assuming that such a final push occurs. Conceivably the industrial system might be eliminated in a somewhat gradual or piecemeal fashion (see paragraphs 4, 167 and Note 4).
32. (Paragraph 193) It is even conceivable (remotely) that the revolution might consist only of a massive change of attitudes toward technology resulting in a relatively gradual and painless disintegration of the industrial system. But if this happens we'll be very lucky. It's far more probably that the transition to a nontechnological society will be very difficult and full of conflicts and disasters.
33. (Paragraph 195) The economic and technological structure of a society are far more important than its political structure in determining the way the average man lives (see paragraphs 95, 119 and Notes 16, 18).
34. (Paragraph 215) This statement refers to our particular brand of anarchism. A wide variety of social attitudes have been called "anarchist," and it may be that many who consider themselves anarchists would not accept our statement of paragraph 215. It should be noted, by the way, that there is a nonviolent anarchist movement whose members probably would not accept FC as anarchist and certainly would not approve of FC's violent methods.
35. (Paragraph 219) Many leftists are motivated also by hostility, but the hostility probably results in part from a frustrated need for power.
36. (Paragraph 229) It is important to understand that we mean someone who sympathizes with these MOVEMENTS as they exist today in our society. One who believes that women, homosexuals, etc., should have equal rights is not necessary a leftist. The feminist, gay rights, etc., movements that exist in our society have the particular ideological tone that characterizes leftism, and if one believes, for example, that women should have equal rights it does not necessarily follow that one must sympathize with the feminist movement as it exists today.
If copyright problems make it impossible for this long quotation to be printed, then please change Note 16 to read as follows:
16. (Paragraph 95) When the American colonies were under British rule there were fewer and less effective legal guarantees of freedom than there were after the American Constitution went into effect, yet there was more personal freedom in pre-industrial America, both before and after the War of Independence, than there was after the Industrial Revolution took hold in this country. In "Violence in America: Historical and Comparative Perspectives," edited by Hugh Davis Graham and Ted Robert Gurr, Chapter 12 by Roger Lane, it is explained how in pre-industrial America the average person had greater independence and autonomy than he does today, and how the process of industrialization necessarily led to the restriction of personal freedom.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Veterano não é dono de bixete
"VETERANO NÃO É DONO DE BIXETE". A frase em letras garrafais chama a atenção dos transeuntes neófitos. Paira sobre um cartaz amarelo que lista várias reclamações contra os "trotes machistas", que, na opinião do responsável pelo cartaz, "não é brincadeira, é opressão".
Eis aí um bizarro exemplo de como são as coisas: primeiro todos os universitários aprovam a idéia do trote, apoiam sua realização e até mesmo desejam sofrer o trote -- com a condição de o poderem aplicar eles mesmos depois --, louvam as maravilhas do mundo universitário, onde a suprema sabedoria se esconde atrás de rituais iniciáticos fora do alcance da imaginação do homem comum e rude, do pobre e do filhinho-de-papai das faculdades privadas; em suma: fomentam os mais baixos, os mais animalescos instintos, a crueldade primordial, destroem em si mesmos e nos colegas quaisquer valores civilizatórios que tivessem sobrado ali, ficando todos indistingüíveis de macacos agressivos e tarados.
Depois vêm aí com um cartaz protestar contra os assédios -- que sem dúvida acontecem em larguíssima escala -- sofridos pelas calouras de 17 anos e que, sendo também novatas no mundo universitário, ainda conservam um pouco de discernimento e pudor.
A incompreensão do fenômeno, porém, é tão grande, que os trotes não são identificados como um problema mental, uma doença que deve ser tratada e eliminada, mas como um sintoma da opressão machista dos homens às mulheres, um produto desta civilização paternalista que, desde que Deus é chamado "o Pai" e não "a Mãe", corrompe a benéfica, pura e angélica natureza do homem primitivo e o torna esta tão torpe criatura.
Na opinião dos autores desse cartaz é preciso, pois, continuar a destruir o que resta da cultura ocidental, e então esperar que haja trotes menos opressores.
-
 @ cd408a69:797e8162
2023-09-14 13:08:47
@ cd408a69:797e8162
2023-09-14 13:08:47Nostrasia Hackathon
Welcome FOSS hackers and creatives who care deeply about freedom technology!
自由のテクノロジーに深い関わりたい FOSS ハッカーとクリエイター、あつまれ!
We're joining forces with Bolt.Fun for a month-long hackathon bridging Bitcoin and NOSTR (Notes and Other Stuff Transmitted by Relays), culminating with a special three day sprint and live event in Tokyo at the Nostrasia Conference.
私たちは、Bolt.Fun と協力して、ビットコインと Nostrを橋渡しする ハッカソンを、1 か月間かけて開催します。 クライマックスは東京で開催されるNostrasia Tokyo が舞台。3日間の特別なスプリントとライブ イベントで最高潮に達します。
Be a Part of the Early Days of Nostr
Nostr の創成期を共に作り上げましょう
Help build the future of Nostr! Like the early days of Bitcoin or of the Internet, Nostr is nascent open technology shaping new types of social experiences to connect people across the globe. It carries a foundation of principles similar to Bitcoin, like decentralization, simplicity, and censorship-resistance.
Nostr の未来を築くのに協力してください!ビットコインやインターネットの初期と同じように、Nostr は世界中の人々をつなぐ新しいソーシャル体験を形成するオープン テクノロジーの初期段階にあります。 Nostr には「分散化」「シンプルさ」「検閲耐性」など、ビットコインと同様の原則が組み込まれています。
Orange-Pill people through the Purple-Nostr-Pill
オレンジピル(ビットコイン)から紫の Nostr のピルへ
Bitcoin and Nostr communities are in synergy. What started as a social protocol is quickly transforming into a space for exploration on ways to support content creators through bitcoin lightning micro payments, often referred to as zaps. Bitcoin integration to the nostr protocol strengthens Bitcoin's use case as a currency of exchange. It carves new paths to a culture of value4value.
ビットコインと Nostr のコミュニティは相乗効果を発揮します。 Nostr はソーシャルプロトコルとしてはじまりましたが、今では Zap (ビットコイン の ライトニング マイクロペイメント)を通じてコンテンツ クリエイターをサポートする方法を模索する空間へと急速に進化しています。 Nostr プロトコルにビットコインが組み合わさることで、交換通貨としてのビットコインの働きが強化されます。 それは、"value4value" の文化への新しい道を切り開くでしょう。
Help People HODL their Keys (Social+Monetary)
人々が自分のキーを HODL (長期保有)できるように支援します (ソーシャル + 金銭的に)
Nostr exists outside of the rule of platforms and those who seek to control them. HODLing your nostr keys is hodling your identity and social graph, outside of KYC. By helping develop and educate on NOSTR, you are helping people escape walled gardens & gain control and choice over their identities & their money. The Internet, over time, has become centralized, help Nostr stay decentralized by supporting the growth of an ecosystem of apps, websites, microapps, relay services...
Nostr はプラットフォームやそれを制御しようとする人々の支配の外にあります。 Nostr keys を持つことは、KYC (本人確認)以外であなたのアイデンティティとソーシャル グラフを保持することになります。 Nostr の開発や教育に貢献することは、人々が束縛から解放され、アイデンティティやお金に対する主導権を得られるよう支援することにもなるのです。 時間の経過とともに集中化されてきたインターネットですが、Nostr のアプリ/Web サイト/マイクロアプリ/リレー サービスのエコシステムの成長をサポートすることで、Nostr の分散化を維持できるようになります。
Permissionless Building
許可を必要としない構築
Opportunities abound in an environment ripe for innovation:
- Develop & design new nostr white label clients, middleware, microapps...
- Help improve existing Nostr FOSS projects
- Contribute directly to protocol development through NIPs (Nostr Implementation Possibilities)
- Encourage nostr and bitcoin adoption through art, education, and any way you like
イノベーションの機が熟した環境には、チャンスが溢れています。
- Nostr の真新しい クライアント、ミドルウェア、マイクロアプリを開発したりデザインする
- 既存の Nostr FOSS プロジェクトの改善に寄与する
- NIP (Nostr Implementation Possibilities) を通じたプロトコル開発に直接貢献する
- 芸術、教育、その他好きな方法を通じて Nostr とビットコインの普及を推進する
Hack in a Supportive Environment
サポートされた環境でハックしよう
We have a growing list of knowledgeable people with skin-in-the-game to mentor and support your journey. Once your project matures, you may also have 1-on-1 guidance to help you reach your vision and discover ways of growing and funding it.
私たちは、あなたの道のりを指導しサポートしてくれる知識豊富なメンターを増やしています。 プロジェクトが成熟した暁には、1対1のガイダンスを受けられる可能性もあります。それは、あなたのビジョンを達成し、成長させて資金を得る方法を発見するのに役立つでしょう。
Nostr has a blossoming community open to innovation. It is also a great testing ground, as people in the community are open to giving and receiving feedback. It is an environment encouraging conversation on feature ideas as well as possible solutions to social media issues and product bugs.
Nostr には、イノベーションに対してオープンで、発展しているコミュニティがあります。 コミュニティの人々はフィードバックの授受にオープンであるため、優れた実験の場にもなります。 機能のアイデアや、ソーシャル メディアの課題や製品のバグの解決策についての会話を促進する環境です。
NostrHack Tracks
You have 3 options
NostrHack Tracks には3つのオプションがあります
Track 1: Builder's Track - Reimagine Nostr
トラック1 : ビルダーのトラック - Nostr を再考しよう
If you can think of it, it can be engineered! Nostr encourages permissionless building while staying mindful of interoperability and network support. Help BUIDL, design, and improve an area you are passionate about. Reimagine and BUIDL features, tools, clients... Help solve issues and create new experiences in social media.
思いつくことができれば、エンジニアリングできる! Nostr は、相互運用性とネットワーク サポートに留意しながら、パーミッションレスな構築 (BUIDL) を奨励しています。 あなたが情熱を注いでいる分野での構築、設計、改善に貢献してください。 機能やツール、クライアントを再考して構築 (BUIDL) し、ソーシャル メディアでの課題を解決して新しい体験を生み出すのに協力してください。
Possibilities...
これを踏まえて…
BUILD on the NOSTR Protocol
The Nostr Implementation Possibilities (NIPs) are optional protocol features anyone can add to their clients. Improve and strengthen existing NIPs or build on new ones. NOSTR is a balance of simplicity, interoperability, backward-compatibility and innovation.
NIPs は、誰でもクライアントに追加できるオプションのプロトコル機能です。 既存の NIP を改善および強化するか、新しい NIP を構築してください。 Nostr は、シンプルさ、相互運用性、下位互換性、革新性のバランスを保っています。
Focus on UX
Nostr is made up of a wide range of clients and tools. To make NOSTR scalable, you can help improve its user experience and education.
Nostr は幅広いクライアントとツールで形成されています。 Nostr をスケーラブルにするために、UX と教育の改善に協力してください。
Help shape a Web of Trust
Nostr cares about removing the KYC tied to our identities. To use Nostr you do not need to give up your phone number, email, financial information, or any metadata tied to your real world identity to be later harvested and sold. You are not the product. What are ways that trust can be earned to prevent impersonation, spam...?
Nostr は、私たちの身元に関連付けられた KYC (個人情報)を取り除けるようにしています。 Nostr を使用しても、電話番号、電子メール、財務情報、または現実世界のアイデンティティに関連付けられたメタデータを、収集されたり販売されたりして手放すことになる心配がありません。 あなたは商品ではないのです。 その中で、なりすましやスパムを防ぐために、信頼を獲得するにはどうすればよいでしょうか...?
NIP05/Nostr address
One of the solutions to build a web of trust used today, is to tie your nostr hex public key to a domain. Although this makes it harder for bots to have nostr addresses, it is not a perfect solution. Domains are centralized through DNS. To help people who do not have their own domains or cannot easily add a NIP05 on their sites, your nostr address can be hosted as a service along with other people's. At this moment, you can highlight just one nostr address per profile. In the future, could it include your website, where you work, and other identifiers... What are other possible solutions?
現在使用されている信頼獲得のための解決策の 1 つは、Nostr の HEX 公開鍵をドメインに結び付けることです。 これにより、完璧な解決策ではないものの、bot などが Nostr アドレスを持つことが難しくなります。 ドメインは DNS を通じて一元化されています。 独自のドメインを持っていない人や、自分では NIP-05 を簡単に追加できない人のために、あなたの Nostr アドレスをサービスとして他の人のものと一緒にホストすることも可能です。 現時点では、プロフィールごとに1つの Nostr アドレスのみを強調表示できますが、将来的には、Web サイト、勤務先、その他の識別情報も含められるようになる可能性があります...この他にも考えられる解決策は何かありますか?
On Decentralization & Discoverability
分散化と発見可能性について
Your identity in NOSTR is tied to your keys, but your information needs to be shared and found across a network of relays. To promote decentralization and censorship resistance, relays need to be easy to setup, lightweight, and sustainable. Relays get to choose what information passes through them, so they are also a form of spam prevention that could potentially also become censoring, so both the relay-runners and the individuals connecting to relays need to have choice and policies cannot be homogenous one-size-fits-all. What are possible solutions to make setting up relays easier, to make running a relay sustainable, to have new ways of discovering information...
Nostr での ID はキーに関連付けられていますが、その情報はリレーのネットワーク全体で共有され、検索できる必要があります。 分散化と検閲耐性を促進するために、リレーはセットアップが簡単で、軽量で、持続可能である必要があります。 リレーは通過する情報を選択できるため、スパム防止の一形態である一方で検閲にもなり得ます。そのため、リレー管理者とリレーに接続する個人の両方に選択権が必要で、ポリシーが全てに対し画一的になってはいけません。 リレーのセットアップを容易にし、リレーの実行を持続可能にし、情報を発見する新しい方法を実現するには、どのような解決策が考えられるでしょうか...?
Buidl tools to connect to Git, as a decentralized alternative to GitHub
GitHub の分散型代替手段として、Git に接続するための BUIDL ツール
Media Uploads
To keep relays lightweight, images are hosted by uploading them to the web, and keeping only the links to them in the data within individual nostr notes. This has led to developing image uploading services specific to nostr, but they carry the risk of centralization or censorship. Some product makers and relay runners are looking into direct uploads to Cloud services. What are possible solutions to the handling of media (images, videos, music...)?
リレーを軽量に保つために、画像は Web にアップロードしてホストされ、各投稿のデータには画像へのリンクのみが保持されます。そんな中で、Nostr に特化した画像アップロード サービスが開発されましたが、集中化や検閲のリスクが伴います。 一部のプロダクト開発者やリレー管理者は、クラウド サービスへの直接アップロードを検討しています。 メディア(画像、ビデオ、音楽など)の処理について、考えられるよい解決策はありますか?
Social Signals
People have the choice to block and mute others, this gives signals to relays, which can reenact policies based on those and other signals. Relays need to be able to differentiate real signals from those wanting to game the system for censorship. Relay runners need to have the capacity to make decisions on what to allow or reject.
ユーザーは他のユーザーをブロックしたりミュートできます。ユーザーの設定内容はリレーに送信され、リレーはその設定に基づいてそれぞれのポリシーを再現できます。 リレーは、実際の設定と、検閲のためにシステムを操作しようとする設定を区別する必要があります。 リレーの管理者には、何を許可し、何を拒否するかを決定する能力が必要です。
Track 2 : Marketplaces & Value4Value
Make freedom of exchange fun again! Nostr extends beyond social. It is integrating ways for content creators to be supported through lightning micropayments, called zaps, for their creations. The possibilities of building niche value4value economies through the exchange of products, services, and ideas, is growing through various avenues: Marketplaces, fundraising, blogs, music, streaming... devise new robust ways of integrating NOSTR and Bitcoin of monetary and skill exchange. Seek to explore distributed, digital reciprocity and free trade. Encourage a culture of value4value.
自由な交流を再び楽しく! Nostr はソーシャルを超えて広がります。 Zap と呼ばれるマイクロペイメントを通じて、コンテンツクリエイターの作品をサポートできる方法を兼ね備えています。 製品、サービス、アイデアの交換を通じてニッチな価値と価値(value4value)の経済を構築する可能性は、さまざまな手段を通じて拡大しています : マーケットプレイス、資金調達、ブログ、音楽、ストリーミングなど... Nostr とビットコインを組み合わせて、金銭とスキルの交換を行う新しい堅牢な方法を考案します。分散型、デジタル相互主義、自由貿易を探究してください。 価値対価値(value4value)の文化を促進してください。
A value4value culture is not only about the individuals using NOSTR products and services, but also about the developers and creatives building sustainable projects. What are ways of sustaining NOSTR through Bitcoin that do NOT make the individual user the product and that are privacy mindful?
value4value の文化は、Nostr の製品やサービスを使用する個人だけでなく、持続可能なプロジェクトを構築する開発者やクリエイターにも関係します。 個人ユーザーを製品にすることなくプライバシーに配慮しながら、ビットコインを通じて Nostr を持続させる方法は何ですか?
Possibilities...
On Social and Economic Signals
Zaps
Many nostr clients have implemented lightning zap payments. Imagine instead of liking a nostr note, you can zap someone's note and they can receive bits/sats in appreciation for their content. It is a strong signal to creators of the kind of content their audiences are looking for. The Apple App Store has recently banned the zapping of specific notes, per Apple's policy that makes the sale of digital content prohibited except when paid through their services. Fortunately, Nostr exists in many decentralized forms outside of app stores and the community is creating new and innovative ways to send bitcoin and free speech from relay to relay, circumventing barriers as they appear. What are solutions that can make NOSTR and zaps ubiquitous?
多くの Nostr クライアントが Zap を導入しています。Nostr での投稿を「いいね」する代わりに Zap すると、その内容に対する感謝としてビットコイン(サトシ)を受け取ることができるイメージです。 これは、フォロワーがどのような種類のコンテンツを求めているかをクリエイターに伝える強力なシグナルになります。 Apple App Storeは最近、サービスを通じて支払われる場合を除きデジタルコンテンツの販売を禁止するというAppleのポリシーに従い、特定の投稿への Zap を禁止しました。 幸い、Nostr は多くが App Store の外で分散型で存在しているため、コミュニティは障壁を回避しながら、ビットコインと言論の自由をリレーからリレーに送信するための革新的な方法を生み出しています。 Nostr と Zaps をユビキタスにするソリューションとは何ですか?
Track 3 : Empower Communities
Give choice and control back to the individual! Create paths forward to help onboard millions of new users and restore free and uncensored speech to the world
選択とコントロールを個人に返そう。 何百万人もの新規ユーザーの参加を支援し、自由で検閲されていない言論を世界に取り戻すための道筋を作り出してください。
Possibilities...
On Security, Privacy & Self-Custody
Private Communication
Direct Messages on NOSTR are encrypted, but metadata is leaked. If someone's key is compromised, whoever has access to that account can read those messages. Integrating secure and reliable encrypted communication protocols, like the SimpleX messaging protocol, is especially desired by the community, as many in Nostr are aware of the risks of surveillance, authoritarianism, government and Big Tech overreach... Private communication is important for individual rights, in particular for activists and journalists across the globe.
Nostr のダイレクト メッセージは暗号化されていますが、メタデータは漏洩します。 誰かのキーが侵害された場合、そのアカウントにアクセスできる人は誰でもそれらのメッセージを読むことができてしまうのです。Nostr の多くの人が監視、権威主義、政府とビッグテックの行き過ぎのリスクを認識しているため、 SimpleX メッセージング プロトコルのような安全で信頼性の高い暗号化通信プロトコルの統合が、コミュニティによって特に望まれています...プライベート通信は個人の権利にとって重要です 、特に世界中の活動家やジャーナリストにとって。
Zaps & Privacy
Current lightning zap payments tend to be custodial and not mindful of privacy, though they are helping onboard people unto lightning. What are ways that people can grow into non-custodial solutions? A wider adoption of Bolt-12 would improve zap payment privacy, what are ways to encourage that development? What are other possible solutions?
現在のザップの支払いは、ライトニングペイメントに出会うのに役立っているものの、カストディアル(管理的)でプライバシーに配慮していない傾向にあります。 ノンカストディアル(非監護的)なものになるよう解決する方法はありませんか? Bolt-12 が広く採用されれば、Zap 支払いのプライバシーが向上しますが、その開発を促進するにはどのような方法がありますか?また、他に考えられる解決策はありませんか?
Closing Live 3-Day Sprint at the Nostrasia Conference
Nostrasia Tokyo 3日間のライブスプリントによる締めくくり
Tokyo | Nov 1-3 (you can also join virtually)
If you heard of the Nostrica unconference, which happened in Costa Rica in March of this year, Nostrasia is the second Nostr World conference, bringing NOSTR and Bitcoin awareness to the heart of Asia, where freedom communication and freedom money are direly needed.
今年の3月にコスタリカで開催された Nostrica のことをご存知の方もいると思いますが、ノストラジアは2回目の Nostr 世界カンファレンスです。自由なコミュニケーションと自由なお金が切実に必要とされているアジアの中心にNostr とビットコインの認識をもたらします。
Tokyo and Hong Kong are beautiful cultural hubs with budding Nostr and thriving Bitcoin communities of their own. We are eager to spread NOSTR education and development in those regions and beyond. We will close this Nostrasia month-long hackathon with a 3-day sprint at the Nostrasia Conference in Tokyo.
東京と香港は、新進気鋭のNostrと繁栄する独自のビットコインコミュニティを持つ美しい文化の中心地です。 私たちは、Nostr の教育と開発をこれらの地域やその他の地域に広めることに熱心に取り組んでいます。 この Nostrasia の 1 か月にわたるハッカソンは、Nostrasia Tokyo での 3 日間のスプリントをもって終了します。
We will have a dedicated workshop area and food for you to hack away on the final details of your projects. On the last day of the conference, the most robust projects will get time on stage to present. We will close the Nostrasia Hackathon with a special presentation.
プロジェクトの最終的な詳細を検討するための専用のワークショップ エリアと食事をご用意します。 カンファレンスの最終日には、最も強力なプロジェクトがステージ上でプレゼンテーションを行う時間が与えられます。 Nostrasia Hackathon は特別なプレゼンテーションで締めくくられます。
We cannot wait to see what new and exciting projects are proposed for the Nostrasia Hackathon. We’re eager to welcome devs and non-devs alike to contribute to this space and help #grownostr in any small way to help onboard Asia, and the rest of the world to this robust open communication protocol and decentralized freedom of speech tool.
Nostrasia Hackathon ではどんな斬新でエキサイティングなプロジェクトが提案されるのか楽しみです。 私たちは、開発者も非開発者も同様にこの分野に貢献し、アジアやその他の世界をこの堅牢なオープン通信プロトコルと分散型言論の自由ツールに参加させるために、どんな小さな方法でも #grownostr を支援してくれることを心から歓迎しています。
-
 @ 2fb77d26:c47a6ee1
2024-12-27 20:10:18
@ 2fb77d26:c47a6ee1
2024-12-27 20:10:18Während ein weiteres Jahr voller Abnormitäten sich dem Ende neigt, ist vieles, das sich im Interesse des nächsten hätte verbessern können, beim Alten geblieben. Denn Veränderungen beginnen im Kopf – und der fungiert bei einer Mehrheit der Artgenossen vor allem als Reservoir für Informationen, Gedanken und Meinungen Dritter. Dritter, die sich die psychischen Schwachstellen der Spezies Mensch gekonnt zunutze machen.
Original mit Quellen: https://www.regenauer.press/der-unsichtbare-dritte
Es war einmal die UNESCO. Diese farbenfroh-inklusiv erscheinende UN-Suborganisation für Erziehung, Wissenschaft und Kultur. Sie wollte »das Undenkbare wenigstens wieder denkbar machen«. So steht es auf Seite 21 des 1946 vom ersten Generaldirektor Julian Huxley verfassten Gründungsdokuments. Gemeint war die Eugenik. Rassenlehre. Die genoss kurz nach Hitler nämlich keinen besonders guten Ruf, sollte uns nach Ansicht von Huxley und Co. jedoch schon bald in überarbeiteter Form als Humangenetik, Bioethik oder biodigitale Konvergenz wieder mit ihren Zuchtprogrammen beglücken dürfen. Mit Transhumanismus. Was Julian Huxley im Rahmen seines im wahrsten Sinne des Wortes wegweisenden Dossiers unterschlug – immerhin prägte er auch den Begriff Transhumanismus – ist die Tatsache, dass die Vereinten Nationen nicht nur »das Undenkbare wieder denkbar machen«, sondern auch »das Denkbare undenkbar machen« wollten.
Die sozialarchitektonischen Vektoren in Richtung einer homogenisierten, pflegeleichten Hominidenbrut – dem Nutzmensch – sind gepflastert mit Stolpersteinen evolutionärer, aufklärerischer Errungenschaften: Selbstbewusstsein und -erhaltungstrieb, Freiheitsdrang, Kreativität, Sozialkompetenz, Empathie, kritisches Denken. All das steht den postmodernen Variationen von Eugenik beharrlich im Weg. Niemand, der originäre Gedanken pflegt, eigene Wege geht und seine Freiheiten schätzt, möchte Teil eines mit der Cloud gekoppelten, genetisch optimierten Kollektivs seelenloser Konformisten werden. Und doch sind es die meisten schon längst. Ob sie Herrschaftsnarrative goutieren, oder Widerstand dagegen leisten – alles, was sie wahrnehmen, diskutieren, verteidigen oder ablehnen stammt aus dem Netz. Es sind limitierte, interpretierte und manipulierte Informationen aus dritter Hand.
Im besten Falle stammen sie noch aus verschiedenen Quellen und erlauben Triangulation zur Bestimmung der eigenen Position. Dazu muss man sich nämlich noch ein paar eigene Gedanken machen. Im schlimmsten Fall wurden sie von Alexa, Siri, dem Google Assistant, ChatGPT oder einem anderen Intelligenz simulierenden Digitalassistenten bereitgestellt, der nur noch eine Antwort serviert. Die richtige. Die Akzeptable. Denn genau das war stets Anspruch der Technokraten. Der langjährige Google-Chef und Bilderberg-Grande Eric Schmidt erklärte schon vor über einem Jahrzehnt, dass »eine Vielzahl von Suchergebnissen ein Fehler und keine Funktion sind«. Das erklärte Ziel von Google sei es, so Schmidt, nur ein einziges Suchergebnis zu präsentieren – das richtige.
Damit solch ein kommunikativer Reduktionismus nicht als Bevormundung, sondern Serviceangebot wahrgenommen wird, muss man verstehen, und steuern, wie Menschen denken. Vielleicht wollte Schmidt aus diesem Grund unbedingt mit Julian Assange über Googles Visionen für eine »neue digitale Welt« sprechen. Mit jemandem, der die technischen Untiefen des Internets kennt – und sie für das Gegenteil dessen nutzt, was Google will. Am 23. Juni 2011 und auf Schmidts Betreiben kam es jedenfalls zu einem geheimen, fünfstündigen Treffen mit dem unter Hausarrest stehenden WikiLeaks-Gründer. Das Transkript dieser Konversation ist erhellend. Vor allem die zweite Hälfte lässt erahnen, wie Schmidt sich die »neue digitale Welt« vorstellt und warum er Ende 2019 konstatierte, dass »Biologie die nächste Grenzverschiebung in puncto Computing ist«.
Google wollte uns nämlich nie informieren, sondern »programmieren«. Das steht so wortwörtlich in internen Dokumenten des Unternehmens, die dank eines Whistleblowers am 24. Juni 2019 den Weg in die Öffentlichkeit fanden. Und wer denkt, »programmieren« beginne erst mit dem Neuralimplantat, dem Chip im Hirn, irrt. Google, Microsoft, Apple, YouTube, Twitter (das ich auch weiterhin so nennen werde), Amazon, Facebook, Wikipedia, Rumble, Instagram, TikTok und Co. schaffen das auch ohne. Denn ihre Algorithmen und Omnipräsenz bestimmen schon jetzt nahezu vollständig, was Menschen wahrnehmen – was sie empört, begeistert, besprechen und bekämpfen. Was nicht bei den großen Portalen, Plattformen und Apps auftaucht, existiert nicht. Ist kein Bestandteil der Realität.
Das gilt gleichermaßen für alles, was Googles Suchmaschine nicht ausspuckt. Entsprechend interessant sind die sogenannten Transparenzberichte des Unternehmens, die veranschaulichen, wie oft staatliche Stellen die Entfernung von Suchergebnissen fordern. Wobei die entsprechenden Listen wohl nur die Spitze der Spitze des Eisbergs darstellen dürften. Nicht umsonst beschäftigen sich weitere geleakte Google-Dokumente primär mit den Zusammenhängen von maschinellem Lernen und menschlicher Wahrnehmung. Mit Nudging und kognitiver Kriegsführung. Das von der CIA gegründete Unternehmen war von Beginn an darauf ausgelegt, die Bevölkerung auszuspionieren, um sie qua Filterblasen zu manipulieren.
Was wir wahrnehmen, ist unsere Realität. Was wir nicht wahrnehmen, wird unsere Realität. Ohne, dass wir etwas dagegen unternehmen könnten. Googles Suchmaschinensegregativ schafft Wirklichkeit. Bei immer noch 91 Prozent Marktanteil ein Kinderspiel. Ganz wie US-Chefstratege Zbigniew Brzezinski es vor 54 Jahren in seinem Buch »Between Two Ages – America's Role in the Technetronic Era« prophezeite.
Was in Abhandlungen zu Verhaltensökonomie blasiert umrissen wird, verblüfft im Alltag durch die Effizienz seiner Profanität: Der zwangsalimentierte Erziehungsfunk repliziert das folgenlose Geschwafel von Politdarstellern, Twitter den von Technokraten kuratierten »Bürgerjournalismus«, Instagram Propaganda von Influencern und Facebook den Tratsch von Oma und Opa. Google präsentiert nur Ergebnisse, die dem Herrschaftsnarrativ dienen, Wikipedia gefährliches Halbwissen von Ideologen, YouTube handzahme Kommentare zum Politspektakel und Rumble die emotionalisierte Replik des vermeintlichen Widerstands. Spotify und Apple Music generieren die Playlist, Amazon schlägt vor, was zu Weihnachten gekauft, Microsoft Word, welche Worte man bei der Formulierung eines Textes meiden und der Krypto-Guru, in welche aus null und eins bestehende »Währung« investiert werden soll. Damit steht das Programm. Die tragenden Wände des Debattenraums. Mehr als dieses Potpourri von Second-Hand-Inhalten haben die meisten Menschen gar nicht mehr im Kopf.
Das Weltwirtschaftsforum (WEF) veröffentlichte im Februar 2022 ein 46 Seiten umfassendes Papier namens »Advancing Digital Agency«, das sich mit der »Macht der Datenvermittler« befasst. Sprich, mit der Rolle der zuvor erwähnten »Dritten« und der Frage, wie Externa zur Verinnerlichung am effektivsten ausgerollt werden können. Der Executive Summary lässt sich auf Seite vier entnehmen:
»Niemand weiß (oder verfolgt), was mit seinen Daten geschieht. (…) Wo Menschen früher Bildschirme zum Navigieren hatten, erzeugen neue Methoden zur Erfassung von Umgebungsdaten mit ihren vielen Vorteilen Nervosität und Resignation, wenn Menschen nicht den Gesamtüberblick haben. Manchmal entscheiden sich Einzelpersonen möglicherweise gegen die Interaktion mit Technologien, die für ihr Leben von großem Nutzen wären. Was aber wäre, wenn man diese Entscheidungspunkte an einen vertrauenswürdigen Agenten auslagern könnte, der im Namen einer Einzelperson oder sogar einer Gruppe handelt? Jetzt, da bildschirmlose Technologie Teil des Alltags ist, bietet sich die Gelegenheit, das Paradigma der Mensch-Technik-Interaktion zu überdenken und die Debatte neu auszurichten, um den Fokus auf Rollen und Verantwortlichkeiten jenseits der Person zu legen. Wie kann der Einsatz von Datenvermittlern Menschen dabei helfen, sich in Technologien und Datenökosystemmodellen zurechtzufinden, ohne aus den Augen zu verlieren, was es bedeutet, Mensch zu sein? (…) Datenvermittler – insbesondere digitale Agenten – stellen einen neuen politischen Hebel dar, mit dem Einzelpersonen die Herausforderungen des wachsenden Datenökosystems möglicherweise meistern können. Dieser Bericht soll Licht auf eine alternative Methode der vermittelten Mensch-Technik-Interaktion werfen, bei der Daten scheinbar nahtlos von Menschen zur Technologie gelangen, und zwar auf eine menschenzentrierte und vor allem vertrauenswürdige Weise. Durch die Kommunikation gemeinsamer Anreize, den Aufbau eines guten Rufs oder die Einholung einer Bestätigung durch Dritte. (…) Dieser Bericht untersucht die Chancen und Risiken von Datenvermittlern und insbesondere digitalen Drittagenten. Von Datentreuhändern bis hin zu vertrauenswürdigen digitalen Agenturen zeichnet der Bericht das Bild einer Welt, die Menschen und Unternehmen gegenüber einfühlsamer ist und durch die Einführung eines vertrauenswürdigen Dritten mehr Sicherheit für den Datenaustausch als Grundlage für Innovationen bietet. Entscheidend ist, dass der Bericht Handlungshebel für den öffentlichen und privaten Sektor vorschlägt, um ein zukunftssicheres digital-politisches Umfeld zu gewährleisten, das einen nahtlosen und vertrauenswürdigen Datenverkehr zwischen Menschen und der Technologie ermöglicht, die ihnen dient.«
Technologie, die uns »dient«? Wer den Buzzword-Neusprech des Davoser Global-Governance-Tentakels zu decodieren weiß, kann sich vorstellen, was mit »dienen« gemeint ist. Denn das Produkt sind wir – die Steuersklaven, DNA-Pools und Datenfarmen. Die Technologie sorgt lediglich für unsere zeitgemäße Versklavung. Sie ist ein maschinell-zentralistisches Monstrum, das sich an unserer Lebenszeit labt. Und die nächsten Jahre dürften darüber entscheiden, ob die Spezies Mensch vor ihrem Fortschritt kapituliert, oder die Oberhand gewinnt. Ob sie auf Generationen hinaus dazu verdammt ist, Vasall ihrer Werkzeuge zu sein, oder diese zu ihrem Vorteil einzusetzen weiß. Denn schlecht sind technische Revolutionen nicht per se. Siehe Blockchain. Lässt man sich von ihnen überrumpeln, allerdings schon.
Und genau das geschieht gerade. Während die leitmediale Deutungselite sich als Megafon moralisierender Selbstgerechtigkeit präsentiert und einer Phase kriegerischer Auseinandersetzungen mit suizidaler Sorglosigkeit entgegensieht, betätigt sich ein guter Teil der kritischen Prominenz als ebenso wirkungsvolles Sedativum für die von Ersteren enttäuschten Massen. Denn am Ende reagiert die jeweilige Klientel auf ein und dieselbe Weise: Sie sitzt auf dem Sofa.
Die tragende Säule der transluzenten Haftanstalt, die ein Habitus lethargischer Bequemlichkeit um uns herum errichtet, ist die Einführung der digitalen Identität. Und die ist in vollem Gange. Australien hat Ende November 2024 als erstes Land der Welt ein Gesetz erlassen, dass Jugendlichen unter 16 Jahren den Zugang zu Social-Media-Portalen untersagt. Und während es sicherlich zu begrüßen ist, dass Kinder ihre Zeit nicht mit digitalem Nonsens verplempern, zeitigt solche Legislatur in letzter Konsequenz nichts anderes als einen Ausweiszwang fürs Internet. Wie sonst soll man feststellen können, wer unter 16 ist? Was eine Frage der Erziehung wäre, gerät in Händen des Staates zu einem Instrument ausufernder Kontrolle.
Auch die Schweiz plant die Einführung einer E-ID – obwohl diese bei einer Volksabstimmung im März 2021 klar abgelehnt wurde. Verfügbar sein soll der digitale Pass ab 2026. Die Nutzung beruhe auf Freiwilligkeit, so die Behörden. Doch schon jetzt werden Stimmen laut, die den Einsatz der digitalen Identität beim Sammeln von Stimmen für politische Begehren fordern. Stichwort »E-Collecting«. Damit soll Unregelmäßigkeiten bei der Vorbereitung von Volksabstimmungen vorgebeugt werden. Die hiesige Piratenpartei hat bereits angekündigt, ein zweites Referendum gegen den elektronischen Ausweis zu lancieren – denn er sei »ein Wolf im Schafspelz«. Die Eidgenossenschaft dürfte in Anbetracht einer erfolgsversprechenden Abstimmungskampagne also noch eine ganze Weile von den negativen Folgen eines solchen Überwachungsinstrumentariums verschont bleiben.
Derweil arbeiten natürlich auch Deutschland, die EU, die USA und das »System Chief Executives Board for Coordination« der UN an einer digitalen Identität. Denn ohne eine solche wird weder das volldigitalisierte Finanzsystem von morgen noch das Mikromanagement der Individualmobilität via CO2-Emissionstracking funktionieren. Keine E-ID, kein digitales Gulag.
Noch lassen sich solche Sachverhalte recherchieren und darstellen. Noch kann Widerstand artikuliert, organisiert und geleistet werden. Doch wenn der Heimcomputer in absehbarer Zeit keine Tastatur mehr hat, weil es nur noch Touchscreens gibt, wenn Gestik, Mimik, Sprachsteuerung und KI das Tippen und Suchen ersetzen, wenn Google nur noch das eine Ergebnis auswirft und der digitale Assistent jede noch so komplexe Frage mit unterkomplexen Monokausalitäten trivialisiert, wenn Plattformen ausgeblendet haben, was die Obrigkeit als »Hassrede« klassifiziert, werden die meisten Menschen gar nicht mehr wissen – und wissen können – was sie nicht wissen. Woher denn auch.
Zensur bedeutet in Zeiten der Plattformökonomie nicht, dass Webseiten gelöscht und Bücher verbrannt werden – Zensur bedeutet, dass Informationen, Artikel und Webseiten einfach nicht mehr angezeigt werden. Dass sie nicht mehr gesucht, gefunden, verlinkt oder zitiert werden können, weil sie nicht mehr Teil des digitalen Ökosystems sind. Zensur beginnt mit Orwells »Memory Hole«, das immer häufiger essenzielle Ressourcen wie das Internetarchiv erfasst. Erst vor wenigen Wochen war die Webseite tagelang offline, weil sie sich einem massiven Hackerangriff ausgesetzt sah. Und auch die Wayback Machine, mit der sich die Historie von Webseiten nachvollziehen lässt, weist immer mehr Löcher auf. So fehlen zum Beispiel alle Einträge des Twitter-Blogs für den Zeitraum vom 3. März 2019 bis zum 28. November 2023. Warum, weiß niemand. Zensur beginnt dort, wo der von Bequemlichkeit, Unwissenheit und Lethargie vereinnahmte Konsument das Internet nur noch via Plattform, Social-Media-Portal und Smartphone-App nutzt, anstatt sich mittels Browser selbst zu orientieren.
Dass genau das schon jetzt gang und gäbe ist, kann ich aus eigener Erfahrung bestätigen. Denn obwohl viele tausend Personen meinen Konten bei Twitter, Telegram und YouTube folgen, hat sich bislang nur etwa ein Zehntel dieser Menge auf meiner Webseite für E-Mail-Updates registriert. Obwohl diese kostenlosen Mail-Updates einen direkten Link zwischen Autor und Leser etablieren und damit »datenvermittelnde« Dritte umgehen. Einen Link, der auch dann noch funktioniert, wenn Social-Media-Konten gesperrt oder gelöscht werden. Wäre das morgen bei mir der Fall, würde vermutlich nur ein Bruchteil meiner »Follower« wissen, wie er meine Webseite findet.
Die diesbezügliche Unselbstständigkeit nimmt teils groteske Formen an. Da fragen Menschen, wo man meine Texte lesen kann, während die URL meines Blogs im nur einen Klick entfernten Profil zu finden ist. Andere posten Fragen, Links oder Screenshots unter Beiträge, die nahelegen, dass sie nicht einmal gelesen haben, was sie kommentieren. Auch eine Suchmaschine scheinen viele nicht mehr aufrufen zu können, wenn sie etwas wissen wollen. Anstatt die gewünschte Information in 30 Sekunden selbst zu recherchieren, stellen sie ihre Frage in Form eines Social-Media-Kommentars und hoffen, dass jemand sie beantwortet. Geschieht das nicht, vergessen sie nach fünf Minuten, dass sie eine Frage hatten.
Es wirkt bisweilen tragisch. Denn auch wer die seit Corona im Aufwind befindlichen neuen Medien, die »kritischen Accounts« und Podcaster verfolgt, macht häufig nichts anderes als der Tagesthemen-Zuschauer: Er konsumiert die Polykrise, als wäre es ein Spielfilm, den man in passiver Schockstarre über sich ergehen lässt.
Aber auch die Medienschaffenden der »fünften Gewalt« unterscheiden sich mithin kaum von ihren Widersachern im leitmedialen Konsenskomplex. Wenn sie nicht gerade mit der eigenen Geschichte oder Opferrolle beschäftigt sind, berichten sie über die Schicksale und Leidenswege von Kollegen. Oder über das, was der Konsenskomplex verlautbaren lässt. Auch die ein oder andere Tirade gegenüber missliebigen Konkurrenten darf nicht fehlen. Hauptsache, es bringt Klicks. Denn wer den Medienzirkus einmal zu seinem Broterwerb gemacht hat, ist abhängig davon, dass er sich auszahlt. Auch wenn es zu Lasten des Inhalts geht.
Kaum jemand recherchiert Fakten, macht Textarbeit, deckt auf, dokumentiert Entwicklungsprozesse, empfiehlt stichhaltige Quellen, liefert neue Themen oder zusätzliche Hintergründe. Kaum ein Format zeichnet sich durch Informationsgehalt aus oder bietet irgendeine Form von Erkenntnisgewinn. Meistens wird einfach das besprochen, kommentiert, analysiert oder eingeordnet – also wiedergekäut – was gerade durch Newsfeeds, Timelines und Trend-Charts geistert.
Eine herausragende Unart ist es, wenn die Moderatoren sich dabei nicht einmal zu schade sind, ihren Twitter-Feed einzublenden, um dann eine Stunde lang geistlos Kommentare von Kommentatoren zu kommentieren. Retorten-Radio. Informativ und intellektuell bereichernd wie die hundertfünfzigste Wiederholung eines Bud-Spencer-Streifens am Weihnachtsfeiertag. Weniger journalistische Relevanz geht kaum.
Wer also nach guten Vorsätzen für das neue Jahr sucht, könnte an exakt dieser Stelle ansetzen. Der Medienschaffende könnte sich auf die Kernaufgabe des Journalismus besinnen und die Mühe machen, zu recherchieren, um seinen Zuschauern und -hörern echten Erkenntnisgewinn zu bescheren. Das macht zwar mehr Arbeit – aber eben auch Sinn.
Und der Konsument könnte damit beginnen, die Kontrolle über seine Informationsgewinnung wiederzuerlangen, anstatt sich berieseln zu lassen wie in alten Zeiten. Zum Beispiel durch die Nutzung eines RSS-Readers, das Lesen von Primärquellen, den Boykott von Big-Tech-Plattformen oder die Anschaffung eines Smartphones mit GrapheneOS-Betriebssystem. Das macht sogar weniger Arbeit, wenn man sich erst einmal eingefuchst hat – und vor allem freier, gelassener und mental resilienter.
Grundsätzlich gilt: Wer nach Lösungen sucht, sollte bei sich selbst beginnen. Denn für die meisten Herausforderungen unserer Zeit existieren sie längst. Nur genutzt werden sie zu selten. Und das liegt nicht an den Lösungen, sondern den Konsumenten, die jeden Tag aufs Neue die Chance verstreichen lassen, es besser zu machen. Wann also wäre ein geeigneterer Zeitpunkt, um den ein oder anderen Neustart zu planen als jetzt, wo sich ein weiteres Jahr in seine letzten, kurzen Tage streckt?
So schwer, verstörend und düster viele davon gewesen sein mögen, so schön, bemerkenswert, erheiternd und licht war manch ein Moment der vergangenen zwölf Monate. Leider ist der menschliche Geist zwecks Risikominimierung evolutionär darauf ausgelegt, sich vor allem an Negatives zu erinnern. Und viel zu oft verdrängen diese unschönen, aber lehrreichen Erfahrungen die Wertschätzung für eine der simpelsten Wahrheiten des Lebens:
Das Schöne zieht seinen Reiz aus der Vergänglichkeit.
Gerade die Flüchtigkeit des Positiven macht es so wichtig, sich diese Erkenntnis zum Ablauf eines Kalenderjahres bewusst zu machen. Denn das wertvollste, was wir Menschen im Lauf eines Lebens sammeln können, sind erhebende Momente. Wie viele wir davon anhäufen bevor unsere eigene Zeit abgelaufen ist, hängt nicht primär von äußeren Umständen, sondern unserer inneren Einstellung ab. Eine den Wirren der Zeit angemessene Sichtweise verbirgt sich hinter einem kurzen, fast schon philosophischen Wortwechsel aus dem für den vorliegenden Text namensgebenden Hitchcock-Streifen:
»Wollen Sie behaupten, Sie hätten Interesse für die Kunst?«
»Ja – für die Kunst weiterzuleben.«
-
 @ e97aaffa:2ebd765d
2024-12-31 16:47:12
@ e97aaffa:2ebd765d
2024-12-31 16:47:12Último dia do ano, momento para tirar o pó da bola de cristal, para fazer reflexões, previsões e desejos para o próximo ano e seguintes.
Ano após ano, o Bitcoin evoluiu, foi ultrapassando etapas, tornou-se cada vez mais mainstream. Está cada vez mais difícil fazer previsões sobre o Bitcoin, já faltam poucas barreiras a serem ultrapassadas e as que faltam são altamente complexas ou tem um impacto profundo no sistema financeiro ou na sociedade. Estas alterações profundas tem que ser realizadas lentamente, porque uma alteração rápida poderia resultar em consequências terríveis, poderia provocar um retrocesso.
Código do Bitcoin
No final de 2025, possivelmente vamos ter um fork, as discussões sobre os covenants já estão avançadas, vão acelerar ainda mais. Já existe um consenso relativamente alto, a favor dos covenants, só falta decidir que modelo será escolhido. Penso que até ao final do ano será tudo decidido.
Depois dos covenants, o próximo foco será para a criptografia post-quantum, que será o maior desafio que o Bitcoin enfrenta. Criar uma criptografia segura e que não coloque a descentralização em causa.
Espero muito de Ark, possivelmente a inovação do ano, gostaria de ver o Nostr a furar a bolha bitcoinheira e que o Cashu tivesse mais reconhecimento pelos bitcoiners.
Espero que surjam avanços significativos no BitVM2 e BitVMX.
Não sei o que esperar das layer 2 de Bitcoin, foram a maior desilusão de 2024. Surgiram com muita força, mas pouca coisa saiu do papel, foi uma mão cheia de nada. Uma parte dos projetos caiu na tentação da shitcoinagem, na criação de tokens, que tem um único objetivo, enriquecer os devs e os VCs.
Se querem ser levados a sério, têm que ser sérios.
“À mulher de César não basta ser honesta, deve parecer honesta”
Se querem ter o apoio dos bitcoiners, sigam o ethos do Bitcoin.
Neste ponto a atitude do pessoal da Ark é exemplar, em vez de andar a chorar no Twitter para mudar o código do Bitcoin, eles colocaram as mãos na massa e criaram o protocolo. É claro que agora está meio “coxo”, funciona com uma multisig ou com os covenants na Liquid. Mas eles estão a criar um produto, vão demonstrar ao mercado que o produto é bom e útil. Com a adoção, a comunidade vai perceber que o Ark necessita dos covenants para melhorar a interoperabilidade e a soberania.
É este o pensamento certo, que deveria ser seguido pelos restantes e futuros projetos. É seguir aquele pensamento do J.F. Kennedy:
“Não perguntem o que é que o vosso país pode fazer por vocês, perguntem o que é que vocês podem fazer pelo vosso país”
Ou seja, não fiquem à espera que o bitcoin mude, criem primeiro as inovações/tecnologia, ganhem adoção e depois demonstrem que a alteração do código camada base pode melhorar ainda mais o vosso projeto. A necessidade é que vai levar a atualização do código.
Reservas Estratégicas de Bitcoin
Bancos centrais
Com a eleição de Trump, emergiu a ideia de uma Reserva Estratégia de Bitcoin, tornou este conceito mainstream. Foi um pivot, a partir desse momento, foram enumerados os políticos de todo o mundo a falar sobre o assunto.
A Senadora Cynthia Lummis foi mais além e propôs um programa para adicionar 200 mil bitcoins à reserva ao ano, até 1 milhão de Bitcoin. Só que isto está a criar uma enorme expectativa na comunidade, só que pode resultar numa enorme desilusão. Porque no primeiro ano, o Trump em vez de comprar os 200 mil, pode apenas adicionar na reserva, os 198 mil que o Estado já tem em sua posse. Se isto acontecer, possivelmente vai resultar numa forte queda a curto prazo. Na minha opinião os bancos centrais deveriam seguir o exemplo de El Salvador, fazer um DCA diário.
Mais que comprar bitcoin, para mim, o mais importante é a criação da Reserva, é colocar o Bitcoin ao mesmo nível do ouro, o impacto para o resto do mundo será tremendo, a teoria dos jogos na sua plenitude. Muitos outros bancos centrais vão ter que comprar, para não ficarem atrás, além disso, vai transmitir uma mensagem à generalidade da população, que o Bitcoin é “afinal é algo seguro, com valor”.
Mas não foi Trump que iniciou esta teoria dos jogos, mas sim foi a primeira vítima dela. É o próprio Trump que o admite, que os EUA necessitam da reserva para não ficar atrás da China. Além disso, desde que os EUA utilizaram o dólar como uma arma, com sanção contra a Rússia, surgiram boatos de que a Rússia estaria a utilizar o Bitcoin para transações internacionais. Que foram confirmados recentemente, pelo próprio governo russo. Também há poucos dias, ainda antes deste reconhecimento público, Putin elogiou o Bitcoin, ao reconhecer que “Ninguém pode proibir o bitcoin”, defendendo como uma alternativa ao dólar. A narrativa está a mudar.
Já existem alguns países com Bitcoin, mas apenas dois o fizeram conscientemente (El Salvador e Butão), os restantes têm devido a apreensões. Hoje são poucos, mas 2025 será o início de uma corrida pelos bancos centrais. Esta corrida era algo previsível, o que eu não esperava é que acontecesse tão rápido.
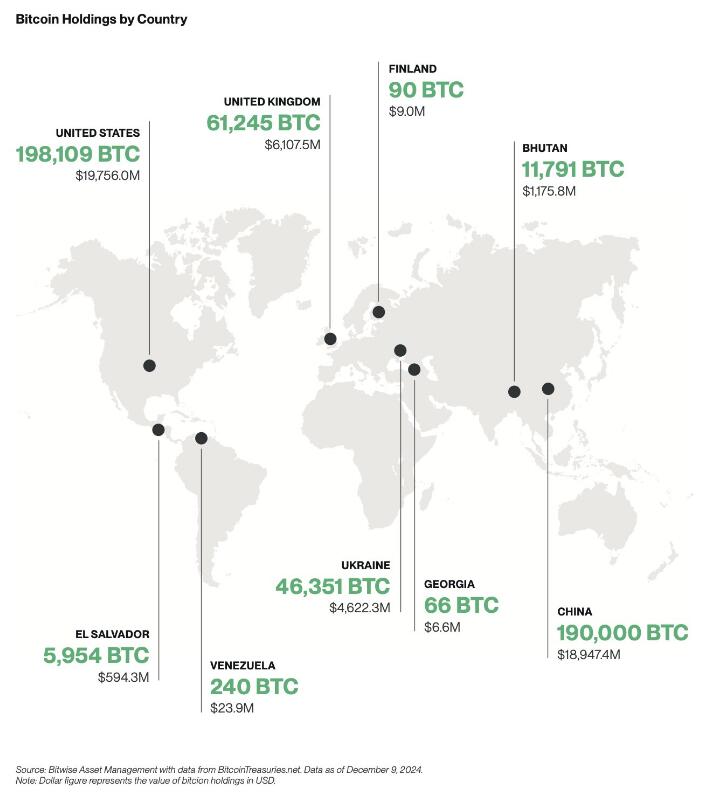
Empresas
A criação de reservas estratégicas não vai ficar apenas pelos bancos centrais, também vai acelerar fortemente nas empresas em 2025.

Mas as empresas não vão seguir a estratégia do Saylor, vão comprar bitcoin sem alavancagem, utilizando apenas os tesouros das empresas, como uma proteção contra a inflação. Eu não sou grande admirador do Saylor, prefiro muito mais, uma estratégia conservadora, sem qualquer alavancagem. Penso que as empresas vão seguir a sugestão da BlackRock, que aconselha um alocações de 1% a 3%.
Penso que 2025, ainda não será o ano da entrada das 6 magníficas (excepto Tesla), será sobretudo empresas de pequena e média dimensão. As magníficas ainda tem uma cota muito elevada de shareholders com alguma idade, bastante conservadores, que têm dificuldade em compreender o Bitcoin, foi o que aconteceu recentemente com a Microsoft.
Também ainda não será em 2025, talvez 2026, a inclusão nativamente de wallet Bitcoin nos sistema da Apple Pay e da Google Pay. Seria um passo gigante para a adoção a nível mundial.
ETFs
Os ETFs para mim são uma incógnita, tenho demasiadas dúvidas, como será 2025. Este ano os inflows foram superiores a 500 mil bitcoins, o IBIT foi o lançamento de ETF mais bem sucedido da história. O sucesso dos ETFs, deve-se a 2 situações que nunca mais se vão repetir. O mercado esteve 10 anos à espera pela aprovação dos ETFs, a procura estava reprimida, isso foi bem notório nos primeiros meses, os inflows foram brutais.
Também se beneficiou por ser um mercado novo, não existia orderbook de vendas, não existia um mercado interno, praticamente era só inflows. Agora o mercado já estabilizou, a maioria das transações já são entre clientes dos próprios ETFs. Agora só uma pequena percentagem do volume das transações diárias vai resultar em inflows ou outflows.
Estes dois fenómenos nunca mais se vão repetir, eu não acredito que o número de inflows em BTC supere os número de 2024, em dólares vai superar, mas em btc não acredito que vá superar.
Mas em 2025 vão surgir uma infindável quantidade de novos produtos, derivativos, novos ETFs de cestos com outras criptos ou cestos com ativos tradicionais. O bitcoin será adicionado em produtos financeiros já existentes no mercado, as pessoas vão passar a deter bitcoin, sem o saberem.
Com o fim da operação ChokePoint 2.0, vai surgir uma nova onda de adoção e de produtos financeiros. Possivelmente vamos ver bancos tradicionais a disponibilizar produtos ou serviços de custódia aos seus clientes.
Eu adoraria ver o crescimento da adoção do bitcoin como moeda, só que a regulamentação não vai ajudar nesse processo.
Preço
Eu acredito que o topo deste ciclo será alcançado no primeiro semestre, posteriormente haverá uma correção. Mas desta vez, eu acredito que a correção será muito menor que as anteriores, inferior a 50%, esta é a minha expectativa. Espero estar certo.
Stablecoins de dólar
Agora saindo um pouco do universo do Bitcoin, acho importante destacar as stablecoins.
No último ciclo, eu tenho dividido o tempo, entre continuar a estudar o Bitcoin e estudar o sistema financeiro, as suas dinâmicas e o comportamento humano. Isto tem sido o meu foco de reflexão, imaginar a transformação que o mundo vai sofrer devido ao padrão Bitcoin. É uma ilusão acreditar que a transição de um padrão FIAT para um padrão Bitcoin vai ser rápida, vai existir um processo transitório que pode demorar décadas.
Com a re-entrada de Trump na Casa Branca, prometendo uma política altamente protecionista, vai provocar uma forte valorização do dólar, consequentemente as restantes moedas do mundo vão derreter. Provocando uma inflação generalizada, gerando uma corrida às stablecoins de dólar nos países com moedas mais fracas. Trump vai ter uma política altamente expansionista, vai exportar dólares para todo o mundo, para financiar a sua própria dívida. A desigualdade entre os pobres e ricos irá crescer fortemente, aumentando a possibilidade de conflitos e revoltas.
“Casa onde não há pão, todos ralham e ninguém tem razão”
Será mais lenha, para alimentar a fogueira, vai gravar os conflitos geopolíticos já existentes, ficando as sociedade ainda mais polarizadas.
Eu acredito que 2025, vai haver um forte crescimento na adoção das stablecoins de dólares, esse forte crescimento vai agravar o problema sistémico que são as stablecoins. Vai ser o início do fim das stablecoins, pelo menos, como nós conhecemos hoje em dia.
Problema sistémico
O sistema FIAT não nasceu de um dia para outro, foi algo que foi construído organicamente, ou seja, foi evoluindo ao longo dos anos, sempre que havia um problema/crise, eram criadas novas regras ou novas instituições para minimizar os problemas. Nestes quase 100 anos, desde os acordos de Bretton Woods, a evolução foram tantas, tornaram o sistema financeiro altamente complexo, burocrático e nada eficiente.
Na prática é um castelo de cartas construído sobre outro castelo de cartas e que por sua vez, foi construído sobre outro castelo de cartas.
As stablecoins são um problema sistémico, devido às suas reservas em dólares e o sistema financeiro não está preparado para manter isso seguro. Com o crescimento das reservas ao longo dos anos, foi se agravando o problema.
No início a Tether colocava as reservas em bancos comerciais, mas com o crescimento dos dólares sob gestão, criou um problema nos bancos comerciais, devido à reserva fracionária. Essas enormes reservas da Tether estavam a colocar em risco a própria estabilidade dos bancos.
A Tether acabou por mudar de estratégia, optou por outros ativos, preferencialmente por títulos do tesouro/obrigações dos EUA. Só que a Tether continua a crescer e não dá sinais de abrandamento, pelo contrário.
Até o próprio mundo cripto, menosprezava a gravidade do problema da Tether/stablecoins para o resto do sistema financeiro, porque o marketcap do cripto ainda é muito pequeno. É verdade que ainda é pequeno, mas a Tether não o é, está no top 20 dos maiores detentores de títulos do tesouros dos EUA e está ao nível dos maiores bancos centrais do mundo. Devido ao seu tamanho, está a preocupar os responsáveis/autoridades/reguladores dos EUA, pode colocar em causa a estabilidade do sistema financeiro global, que está assente nessas obrigações.
Os títulos do tesouro dos EUA são o colateral mais utilizado no mundo, tanto por bancos centrais, como por empresas, é a charneira da estabilidade do sistema financeiro. Os títulos do tesouro são um assunto muito sensível. Na recente crise no Japão, do carry trade, o Banco Central do Japão tentou minimizar a desvalorização do iene através da venda de títulos dos EUA. Esta operação, obrigou a uma viagem de emergência, da Secretaria do Tesouro dos EUA, Janet Yellen ao Japão, onde disponibilizou liquidez para parar a venda de títulos por parte do Banco Central do Japão. Essa forte venda estava desestabilizando o mercado.
Os principais detentores de títulos do tesouros são institucionais, bancos centrais, bancos comerciais, fundo de investimento e gestoras, tudo administrado por gestores altamente qualificados, racionais e que conhecem a complexidade do mercado de obrigações.
O mundo cripto é seu oposto, é naife com muita irracionalidade e uma forte pitada de loucura, na sua maioria nem faz a mínima ideia como funciona o sistema financeiro. Essa irracionalidade pode levar a uma “corrida bancária”, como aconteceu com o UST da Luna, que em poucas horas colapsou o projeto. Em termos de escala, a Luna ainda era muito pequena, por isso, o problema ficou circunscrito ao mundo cripto e a empresas ligadas diretamente ao cripto.
Só que a Tether é muito diferente, caso exista algum FUD, que obrigue a Tether a desfazer-se de vários biliões ou dezenas de biliões de dólares em títulos num curto espaço de tempo, poderia provocar consequências terríveis em todo o sistema financeiro. A Tether é grande demais, é já um problema sistémico, que vai agravar-se com o crescimento em 2025.
Não tenham dúvidas, se existir algum problema, o Tesouro dos EUA vai impedir a venda dos títulos que a Tether tem em sua posse, para salvar o sistema financeiro. O problema é, o que vai fazer a Tether, se ficar sem acesso às venda das reservas, como fará o redeem dos dólares?
Como o crescimento do Tether é inevitável, o Tesouro e o FED estão com um grande problema em mãos, o que fazer com o Tether?
Mas o problema é que o atual sistema financeiro é como um curto cobertor: Quanto tapas a cabeça, destapas os pés; Ou quando tapas os pés, destapas a cabeça. Ou seja, para resolver o problema da guarda reservas da Tether, vai criar novos problemas, em outros locais do sistema financeiro e assim sucessivamente.
Conta mestre
Uma possível solução seria dar uma conta mestre à Tether, dando o acesso direto a uma conta no FED, semelhante à que todos os bancos comerciais têm. Com isto, a Tether deixaria de necessitar os títulos do tesouro, depositando o dinheiro diretamente no banco central. Só que isto iria criar dois novos problemas, com o Custodia Bank e com o restante sistema bancário.
O Custodia Bank luta há vários anos contra o FED, nos tribunais pelo direito a ter licença bancária para um banco com full-reserves. O FED recusou sempre esse direito, com a justificativa que esse banco, colocaria em risco toda a estabilidade do sistema bancário existente, ou seja, todos os outros bancos poderiam colapsar. Perante a existência em simultâneo de bancos com reserva fracionária e com full-reserves, as pessoas e empresas iriam optar pelo mais seguro. Isso iria provocar uma corrida bancária, levando ao colapso de todos os bancos com reserva fracionária, porque no Custodia Bank, os fundos dos clientes estão 100% garantidos, para qualquer valor. Deixaria de ser necessário limites de fundos de Garantia de Depósitos.
Eu concordo com o FED nesse ponto, que os bancos com full-reserves são uma ameaça a existência dos restantes bancos. O que eu discordo do FED, é a origem do problema, o problema não está nos bancos full-reserves, mas sim nos que têm reserva fracionária.
O FED ao conceder uma conta mestre ao Tether, abre um precedente, o Custodia Bank irá o aproveitar, reclamando pela igualdade de direitos nos tribunais e desta vez, possivelmente ganhará a sua licença.
Ainda há um segundo problema, com os restantes bancos comerciais. A Tether passaria a ter direitos similares aos bancos comerciais, mas os deveres seriam muito diferentes. Isto levaria os bancos comerciais aos tribunais para exigir igualdade de tratamento, é uma concorrência desleal. Isto é o bom dos tribunais dos EUA, são independentes e funcionam, mesmo contra o estado. Os bancos comerciais têm custos exorbitantes devido às políticas de compliance, como o KYC e AML. Como o governo não vai querer aliviar as regras, logo seria a Tether, a ser obrigada a fazer o compliance dos seus clientes.
A obrigação do KYC para ter stablecoins iriam provocar um terramoto no mundo cripto.
Assim, é pouco provável que seja a solução para a Tether.
FED
Só resta uma hipótese, ser o próprio FED a controlar e a gerir diretamente as stablecoins de dólar, nacionalizado ou absorvendo as existentes. Seria uma espécie de CBDC. Isto iria provocar um novo problema, um problema diplomático, porque as stablecoins estão a colocar em causa a soberania monetária dos outros países. Atualmente as stablecoins estão um pouco protegidas porque vivem num limbo jurídico, mas a partir do momento que estas são controladas pelo governo americano, tudo muda. Os países vão exigir às autoridades americanas medidas que limitem o uso nos seus respectivos países.
Não existe uma solução boa, o sistema FIAT é um castelo de cartas, qualquer carta que se mova, vai provocar um desmoronamento noutro local. As autoridades não poderão adiar mais o problema, terão que o resolver de vez, senão, qualquer dia será tarde demais. Se houver algum problema, vão colocar a responsabilidade no cripto e no Bitcoin. Mas a verdade, a culpa é inteiramente dos políticos, da sua incompetência em resolver os problemas a tempo.
Será algo para acompanhar futuramente, mas só para 2026, talvez…
É curioso, há uns anos pensava-se que o Bitcoin seria a maior ameaça ao sistema ao FIAT, mas afinal, a maior ameaça aos sistema FIAT é o próprio FIAT(stablecoins). A ironia do destino.
Isto é como uma corrida, o Bitcoin é aquele atleta que corre ao seu ritmo, umas vezes mais rápido, outras vezes mais lento, mas nunca pára. O FIAT é o atleta que dá tudo desde da partida, corre sempre em velocidade máxima. Só que a vida e o sistema financeiro não é uma prova de 100 metros, mas sim uma maratona.
Europa
2025 será um ano desafiante para todos europeus, sobretudo devido à entrada em vigor da regulamentação (MiCA). Vão começar a sentir na pele a regulamentação, vão agravar-se os problemas com os compliance, problemas para comprovar a origem de fundos e outras burocracias. Vai ser lindo.
O Travel Route passa a ser obrigatório, os europeus serão obrigados a fazer o KYC nas transações. A Travel Route é uma suposta lei para criar mais transparência, mas prática, é uma lei de controle, de monitorização e para limitar as liberdades individuais dos cidadãos.
O MiCA também está a colocar problemas nas stablecoins de Euro, a Tether para já preferiu ficar de fora da europa. O mais ridículo é que as novas regras obrigam os emissores a colocar 30% das reservas em bancos comerciais. Os burocratas europeus não compreendem que isto coloca em risco a estabilidade e a solvência dos próprios bancos, ficam propensos a corridas bancárias.
O MiCA vai obrigar a todas as exchanges a estar registadas em solo europeu, ficando vulnerável ao temperamento dos burocratas. Ainda não vai ser em 2025, mas a UE vai impor políticas de controle de capitais, é inevitável, as exchanges serão obrigadas a usar em exclusividade stablecoins de euro, as restantes stablecoins serão deslistadas.
Todas estas novas regras do MiCA, são extremamente restritas, não é para garantir mais segurança aos cidadãos europeus, mas sim para garantir mais controle sobre a população. A UE está cada vez mais perto da autocracia, do que da democracia. A minha única esperança no horizonte, é que o sucesso das políticas cripto nos EUA, vai obrigar a UE a recuar e a aligeirar as regras, a teoria dos jogos é implacável. Mas esse recuo, nunca acontecerá em 2025, vai ser um longo período conturbado.
Recessão
Os mercados estão todos em máximos históricos, isto não é sustentável por muito tempo, suspeito que no final de 2025 vai acontecer alguma correção nos mercados. A queda só não será maior, porque os bancos centrais vão imprimir dinheiro, muito dinheiro, como se não houvesse amanhã. Vão voltar a resolver os problemas com a injeção de liquidez na economia, é empurrar os problemas com a barriga, em de os resolver. Outra vez o efeito Cantillon.
Será um ano muito desafiante a nível político, onde o papel dos políticos será fundamental. A crise política na França e na Alemanha, coloca a UE órfã, sem um comandante ao leme do navio. 2025 estará condicionado pelas eleições na Alemanha, sobretudo no resultado do AfD, que podem colocar em causa a propriedade UE e o euro.
Possivelmente, só o fim da guerra poderia minimizar a crise, algo que é muito pouco provável acontecer.
Em Portugal, a economia parece que está mais ou menos equilibrada, mas começam a aparecer alguns sinais preocupantes. Os jogos de sorte e azar estão em máximos históricos, batendo o recorde de 2014, época da grande crise, não é um bom sinal, possivelmente já existe algum desespero no ar.
A Alemanha é o motor da Europa, quanto espirra, Portugal constipa-se. Além do problema da Alemanha, a Espanha também está à beira de uma crise, são os países que mais influenciam a economia portuguesa.
Se existir uma recessão mundial, terá um forte impacto no turismo, que é hoje em dia o principal motor de Portugal.
Brasil
Brasil é algo para acompanhar em 2025, sobretudo a nível macro e a nível político. Existe uma possibilidade de uma profunda crise no Brasil, sobretudo na sua moeda. O banco central já anda a queimar as reservas para minimizar a desvalorização do Real.

Sem mudanças profundas nas políticas fiscais, as reservas vão se esgotar. As políticas de controle de capitais são um cenário plausível, será interesse de acompanhar, como o governo irá proceder perante a existência do Bitcoin e stablecoins. No Brasil existe um forte adoção, será um bom case study, certamente irá repetir-se em outros países num futuro próximo.
Os próximos tempos não serão fáceis para os brasileiros, especialmente para os que não têm Bitcoin.
Blockchain
Em 2025, possivelmente vamos ver os primeiros passos da BlackRock para criar a primeira bolsa de valores, exclusivamente em blockchain. Eu acredito que a BlackRock vai criar uma própria blockchain, toda controlada por si, onde estarão os RWAs, para fazer concorrência às tradicionais bolsas de valores. Será algo interessante de acompanhar.
Estas são as minhas previsões, eu escrevi isto muito em cima do joelho, certamente esqueci-me de algumas coisas, se for importante acrescentarei nos comentários. A maioria das previsões só acontecerá após 2025, mas fica aqui a minha opinião.
Isto é apenas a minha opinião, Don’t Trust, Verify!
-
 @ bcea2b98:7ccef3c9
2025-01-02 17:47:27
@ bcea2b98:7ccef3c9
2025-01-02 17:47:27originally posted at https://stacker.news/items/833889
-
 @ 9f94e6cc:f3472946
2024-11-21 18:55:12
@ 9f94e6cc:f3472946
2024-11-21 18:55:12Der Entartungswettbewerb TikTok hat die Jugend im Griff und verbrutzelt ihre Hirne. Über Reels, den Siegeszug des Hochformats und die Regeln der Viralität.
Text: Aron Morhoff
Hollywood steckt heute in der Hosentasche. 70 Prozent aller YouTube-Inhalte werden auf mobilen Endgeräten, also Smartphones, geschaut. Instagram und TikTok sind die angesagtesten Anwendungen für junge Menschen. Es gibt sie nur noch als App, und ihr Design ist für Mobiltelefone optimiert.
Einst waren Rechner und Laptops die Tools, mit denen ins Internet gegangen wurde. Auch als das Smartphone seinen Siegeszug antrat, waren die Sehgewohnheiten noch auf das Querformat ausgerichtet. Heute werden Rechner fast nur noch zum Arbeiten verwendet. Das Berieseln, die Unterhaltung, das passive Konsumieren hat sich vollständig auf die iPhones und Samsungs dieser Welt verlagert. Das Telefon hat den aufrechten Gang angenommen, kaum einer mehr hält sein Gerät waagerecht.
Homo Digitalis Erectus
Die Welt steht also Kopf. Die Form eines Mediums hat Einfluss auf den Inhalt. Marshall McLuhan formulierte das so: Das Medium selbst ist die Botschaft. Ja mei, mag sich mancher denken, doch medienanthropologisch ist diese Entwicklung durchaus eine Betrachtung wert. Ein Querformat eignet sich besser, um Landschaften, einen Raum oder eine Gruppe abzubilden. Das Hochformat entspricht grob den menschlichen Maßen von der Hüfte bis zum Kopf. Der TikTok-Tanz ist im Smartphone-Design also schon angelegt. Das Hochformat hat die Medieninhalte unserer Zeit noch narzisstischer gemacht.
Dass wir uns durch Smartphones freizügiger und enthemmter zur Schau stellen, ist bekannt. 2013 wurde „Selfie“ vom Oxford English Dictionary zum Wort des Jahres erklärt. Selfie, Selbstporträt, Selbstdarstellung.
Neu ist der Aufwand, der heute vonnöten ist, um die Aufmerksamkeitsschwelle der todamüsierten Mediengesellschaft überhaupt noch zu durchbrechen. In beängstigender Hypnose erwischt man viele Zeitgenossen inzwischen beim Doomscrollen. Das ist der Fachbegriff für das weggetretene Endloswischen und erklärt auch den Namen „Reel“: Der Begriff, im Deutschen verwandt mit „Rolle“, beschreibt die Filmrolle, von der 24 Bilder pro Sekunde auf den Projektor gewischt oder eben abgespult werden.
Länger als drei Sekunden darf ein Kurzvideo deshalb nicht mehr gehen, ohne dass etwas Aufregendes passiert. Sonst wird das Reel aus Langeweile weggewischt. Die Welt im Dopamin-Rausch. Für den Ersteller eines Videos heißt das inzwischen: Sei der lauteste, schrillste, gestörteste Marktschreier. Das Wettrennen um die Augäpfel zwingt zu extremen Formen von Clickbait.
15 Sekunden Ruhm
Das nimmt inzwischen skurrile Formen an. Das Video „Look who I found“ von Noel Robinson (geboren 2001) war im letzten Jahr einer der erfolgreichsten deutschen TikTok-Clips. Man sieht den Deutsch-Nigerianer beim Antanzen eines karikaturartig übergewichtigen Menschen. Noel wird geschubst und fällt. Daraufhin wechselt das Lied – und der fette Mann bewegt seinen Schwabbelbauch im Takt. Noel steht wieder auf, grinst, beide tanzen gemeinsam. Das dauert 15 Sekunden. Ich rate Ihnen, sich das Video einmal anzuschauen, um die Mechanismen von TikTok zu verstehen. Achten Sie alleine darauf, wie vielen Reizen (Menschenmenge, Antanzen, Sturz, Schwabbelbauch) Sie in den ersten fünf Sekunden ausgesetzt sind. Wer schaut so was? Bis dato 220 Millionen Menschen. Das ist kapitalistische Verwertungslogik im bereits verwesten Endstadium. Adorno oder Fromm hätten am Medienzeitgeist entweder ihre Freude oder mächtig zu knabbern.
Die Internet- und Smartphoneabdeckung beträgt mittlerweile fast 100 Prozent. Das Überangebot hat die Regeln geändert. Um überhaupt gesehen zu werden, muss man heute viral gehen. Was dafür inzwischen nötig ist, spricht die niedrigsten Bedürfnisse des Menschen an: Gewalt, Ekel, Sexualisierung, Schock. Die jungen Erwachsenen, die heute auf sozialen Netzwerken den Ton angeben, haben diese Mechanismen längst verinnerlicht. Wie bewusst ihnen das ist, ist fraglich. 2024 prallt eine desaströse Bildungssituation samt fehlender Medienkompetenz auf eine egomanische Jugend, die Privatsphäre nie gekannt hat und seit Kindesbeinen alles in den Äther ballert, was es festhalten kann. Man muss kein Kulturpessimist sein, um diese degenerative Dynamik, auch in ihrer Implikation für unser Zusammenleben und das psychische Wohlergehen der Generation TikTok, als beängstigend zu bezeichnen.
Aron Morhoff studierte Medienethik und ist Absolvent der Freien Akademie für Medien & Journalismus. Frühere Stationen: RT Deutsch und Nuoviso. Heute: Stichpunkt Magazin, Manova, Milosz Matuschek und seine Liveshow "Addictive Programming".
-
 @ ccc8ee23:9f3d9783
2024-12-19 05:55:09
@ ccc8ee23:9f3d9783
2024-12-19 05:55:09Chef's notes
Dare to taste the bold? One bite of Jengkol Balado and you’ll be hooked
Spicy Jengkol Balado - Betawi Style A traditional dish from Betawi (Jakarta), Jengkol Balado is nutty bold and aromatic delicacy made with jengkol beans. This version uses thinly sliced jengkol for a delightful texture.
Serve it with a plate of steamed fragrant white rice and a side of crunchy cucumber for a complete meal that satisfies on every level.
Details
- 🍳 Cook time: 40 min
- 🍽️ Servings: 2
Ingredients
- Jengkol 250 grams
- Chilli 100 grams
- Shallot 5 cloves
- Garlic 2 cloves
- Tomato 1 clove (small)
- Bay leaves 2
- Galangal 2cm. Bruished
- Veggie oil 20ml or 4 tsp
- Seasoning
Directions
- Prepare the Jengkol Wash the jengkol thoroughly and slice it thinly. Boil the slices in water with the bay leaves for 10–15 minutes to soften and reduce their strong odour. Drain and set aside.
- Make the Balado Paste. Blend chillies, shallots, garlic, candlenut and tomatoes into a slightly coarse paste using a blender
- Heat oil in a pan and sauté the balado paste until fragrant and the oil starts to separate. Add the galangal, bay leaves, salt, sugar, and seasoning. Stir well
- Add jengkol to the pan. Mix until jengkol are fully coated in the balado paste.
- If the mixture seems too dry, add a splash of water and let it simmer on low heat to allow the flavours to infuse.
- Taste the dish and adjust the seasoning with more salt or sugar if needed.
- Remove from heat and serve hot with steamed rice.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28neuron.vim
I started using this neuron thing to create an update this same zettelkasten, but the existing vim plugin had too many problems, so I forked it and ended up changing almost everything.
Since the upstream repository was somewhat abandoned, most users and people who were trying to contribute upstream migrate to my fork too.
-
 @ ac8bb9b0:70278acc
2024-12-18 21:18:57
@ ac8bb9b0:70278acc
2024-12-18 21:18:57Details
- ⏲️ Prep time: 10
- 🍳 Cook time: 20
- 🍽️ Servings: 5
Ingredients
- 8 ounces uncooked linguine
- 1 pound chicken breast, cut into strips
- 1-2 tsp Cajun seasoning, or more to taste
- 1 tsp garlic powder
- 1 tbsp extra virgin olive oil
- 1 medium red bell pepper, thinly sliced
- 1 medium yellow bell pepper, thinly sliced
- 8 oz fresh mushrooms, sliced
- 1/2 red onion, sliced
- 3 cloves garlic, minced
- 2 tomatoes, diced
- 1 cup low sodium chicken broth
- 1/3 cup skim milk
- 1 tbsp flour
- 3 tbsp light cream cheese
- fresh cracked pepper
- 2 scallions, chopped
- kosher salt to taste
- avocado oil spray
Directions
- Prep all your vegetables.
- In a small blender make a slurry by combining milk, flour and cream cheese. Set aside.
- Season chicken generously with Cajun seasoning, garlic powder and salt.
- Prepare pasta in salted water according to package directions.
- Heat a large heavy nonstick skillet over medium-high heat; spray with oil and add half of the chicken.
- Sauté 5 to 6 minutes or until done, set aside on a plate and repeat with the remaining chicken. Set aside.
- Add olive oil to the skillet and reduce to medium; add bell peppers, onions, and garlic to skillet, sauté 3-4 minutes.
- Add mushrooms and tomatoes and sauté 3-4 more minutes or until vegetables are tender.
- Season with 1/4 tsp salt, garlic powder and fresh cracked pepper to taste.
- Reduce heat to medium-low; add chicken broth and pour in slurry stirring about 2 minutes.
- Return chicken to skillet; adjust salt and Cajun seasoning to taste, cook another minute or two until hot, then add linguine; toss well to coat.
- Top with chopped scallions and enjoy!
-
 @ f9cf4e94:96abc355
2024-12-30 19:02:32
@ f9cf4e94:96abc355
2024-12-30 19:02:32Na era das grandes navegações, piratas ingleses eram autorizados pelo governo para roubar navios.
A única coisa que diferenciava um pirata comum de um corsário é que o último possuía a “Carta do Corso”, que funcionava como um “Alvará para o roubo”, onde o governo Inglês legitimava o roubo de navios por parte dos corsários. É claro, que em troca ele exigia uma parte da espoliação.
Bastante similar com a maneira que a Receita Federal atua, não? Na verdade, o caso é ainda pior, pois o governo fica com toda a riqueza espoliada, e apenas repassa um mísero salário para os corsários modernos, os agentes da receita federal.
Porém eles “justificam” esse roubo ao chamá-lo de imposto, e isso parece acalmar os ânimos de grande parte da população, mas não de nós. Não é por acaso que 'imposto' é o particípio passado do verbo 'impor'. Ou seja, é aquilo que resulta do cumprimento obrigatório -- e não voluntário -- de todos os cidadãos. Se não for 'imposto' ninguém paga. Nem mesmo seus defensores. Isso mostra o quanto as pessoas realmente apreciam os serviços do estado.
Apenas volte um pouco na história: os primeiros pagadores de impostos eram fazendeiros cujos territórios foram invadidos por nômades que pastoreavam seu gado. Esses invasores nômades forçavam os fazendeiros a lhes pagar uma fatia de sua renda em troca de "proteção". O fazendeiro que não concordasse era assassinado.
Os nômades perceberam que era muito mais interessante e confortável apenas cobrar uma taxa de proteção em vez de matar o fazendeiro e assumir suas posses. Cobrando uma taxa, eles obtinham o que necessitavam. Já se matassem os fazendeiros, eles teriam de gerenciar por conta própria toda a produção da fazenda. Daí eles entenderam que, ao não assassinarem todos os fazendeiros que encontrassem pelo caminho, poderiam fazer desta prática um modo de vida.
Assim nasceu o governo.
Não assassinar pessoas foi o primeiro serviço que o governo forneceu. Como temos sorte em ter à nossa disposição esta instituição!
Assim, não deixa de ser curioso que algumas pessoas digam que os impostos são pagos basicamente para impedir que aconteça exatamente aquilo que originou a existência do governo. O governo nasceu da extorsão. Os fazendeiros tinham de pagar um "arrego" para seu governo. Caso contrário, eram assassinados. Quem era a real ameaça? O governo. A máfia faz a mesma coisa.
Mas existe uma forma de se proteger desses corsários modernos. Atualmente, existe uma propriedade privada que NINGUÉM pode tirar de você, ela é sua até mesmo depois da morte. É claro que estamos falando do Bitcoin. Fazendo as configurações certas, é impossível saber que você tem bitcoin. Nem mesmo o governo americano consegue saber.
brasil #bitcoinbrasil #nostrbrasil #grownostr #bitcoin
-
 @ 101b30ee:18a46a45
2025-01-02 17:28:15
@ 101b30ee:18a46a45
2025-01-02 17:28:15
ハンドシェイク
- HTTPリクエスト解析
- [ ] HTTPリクエストラインのパーサー関数作成
- [x] HTTPヘッダーのパーサー関数作成
- [ ] HTTPリクエストボディのパーサー関数作成
- [ ] WebSocket関連ヘッダーの検証
- [ ]
Upgrade: websocket - [ ]
Connection: Upgrade - [ ]
Sec-WebSocket-Keyの取得と検証 - [ ]
Sec-WebSocket-Version: 13の検証
- [ ]
- HTTPレスポンス作成
- [ ]
Sec-WebSocket-Acceptの生成- [x]
Sec-WebSocket-KeyにSHA-1適用(外部依存) - [ ]
Sec-WebSocket-KeyにSHA-1適用(非依存) - [x]
Sec-WebSocket-KeyにBase64エンコードを適用
- [x]
- [x] HTTP 101 Switching Protocolsレスポンスの構築と送信
データ転送
WebSocketフレームの処理
- フレーム解析
- [x]
finビットの取り出しと解釈 - [x]
rsv1,rsv2,rsv3の取り出しと検証 - [ ]
opcodeの取り出しと処理- [ ] 0x0: 継続フレーム
- [ ] 0x1: テキストフレーム
- [ ] 0x2: バイナリフレーム
- [ ] 0x8: 接続終了
- [ ] 0x9: Ping
- [ ] 0xA: Pong
- [x]
maskフラグの取得と検証 - [x]
payload_lenの取り出しと解析 - [x] 拡張されたペイロード長(
extended payload len)の取り出し - [x]
masking keyの取得とデコード - [x]
payloadデータの取り出し - [ ]
finに基づく分割パケット対応 - デコード
- [x]
masking keyを使用したペイロードデコード - opcode別処理
- [ ] テキストフレーム(0x1)のUTF-8デコードと処理
- [ ] バイナリフレーム(0x2)のデータ処理
- [ ] Ping(0x9)フレームへのPong応答
- [ ] 接続終了(0x8)の処理
- [ ] 不正なopcodeに対するエラー応答
フレーム生成
- フレーム構築
- [ ]
finフラグ設定 - [ ]
opcodeの設定 - [ ] ペイロードのマスキング処理(クライアント向けのみ)
- [ ] ペイロード長の設定(拡張ペイロード長を含む)
- [ ] フレーム全体のバイトストリーム化
接続管理
- [x] クライアント接続の確立
- [x] 2クライアント以上の接続の確立
- [ ] 接続中のクライアントのリスト管理
- [ ] 接続のタイムアウト処理
- [ ] 不正なクライアントからの接続拒否
- [ ] 接続終了時のクリーンアップ処理
- [ ] ハートビート機能(Ping/Pong)による接続維持
セキュリティ
- [ ] WebSocket Originヘッダーの検証(許可されたオリジンのみ受け入れる)
- [ ] メッセージサイズの上限設定(大規模メッセージ攻撃の防御)
- [ ] 不正なフレーム/データに対するエラーハンドリング
- [ ] SSL/TLSサポート(wssプロトコル用)
拡張機能とプロトコルアップグレード
- [ ] サブプロトコル(Sec-WebSocket-Protocol)の処理
- [ ] 拡張(Sec-WebSocket-Extensions)のサポート
- 圧縮データのデコード (例: permessage-deflate)
テストとデバッグ
- [ ] 単体テスト
- [ ] ハンドシェイクのテスト
- [ ] フレーム解析と生成のテスト
- [ ] 各opcode処理のテスト
- [ ] 負荷テスト(高負荷時の動作確認)
- [ ] プロトコルコンフォーマンステスト
- [ ] RFC 6455に準拠しているかの確認
- [ ] ロギングとデバッグツールの実装
ドキュメント
- [ ] コードベースのコメントとドキュメント化
- [ ] WebSocketサーバーの設定と使用法についてのユーザーガイド作成
タグ
RFC6455
-
 @ ac8bb9b0:70278acc
2024-12-16 19:37:12
@ ac8bb9b0:70278acc
2024-12-16 19:37:12Details
- ⏲️ Prep time: 10
- 🍳 Cook time: 20
- 🍽️ Servings: 6
Ingredients
- 2 tablespoons extra virgin olive oil
- 1 1/2 pounds ground chicken
- 1 yellow onion, chopped
- 2 tablespoons taco seasoning
- salt and black pepper
- 2 1/2 cups salsa or enchilada sauce
- 1 chipotle chili in adobo, chopped
- 2 cups fresh corn
- 4 ounces cream cheese, at room temperature
- 1/4 cup plain greek yogurt
- 1 teaspoon chili powder
- 1 1/2 cups shredded Mexican cheese blend
- 2 cups tortilla chips
- avocado, cilantro, and green onions, for serving
Directions
- Preheat the oven to 400° F.
- In a large oven-safe skillet, combine the olive oil, chicken, onion, salt, and pepper. Set the skillet over high heat. Cook, breaking up the meat as it cooks, until browned all over, 5 minutes. Add the taco seasoning, cook another 2 minutes. Then add 1/2 cup water. Stir in the salsa/enchilada sauce and chipotle. Simmer 5 minutes. Remove from the heat and add in the cilantro.
- In a bowl, combine the corn, cream cheese, yogurt, chili powder, and salt. Stir in 1/2 cup cheese.
- Dollop 1/3 of the corn mix over the skillet. Add the tortilla chips on top, pressing them gently into the skillet. Add the remaining corn mix by spoonfuls on top of the chips (like nachos). Top with the remaining cheese. Bake for 15 minutes, until the cheese is melted.
- Serve topped as desired with avocado, cilantro, green onion, and cotija/feta cheese.
-
 @ 42342239:1d80db24
2024-12-22 09:07:27
@ 42342239:1d80db24
2024-12-22 09:07:27Knappheit statt Slogans: eine Dosis ökonomischer Realität für die politischen Debatten
Die EU-Wirtschaft steht vor zahlreichen Herausforderungen, von hohen Energiekosten bis hin zu geringer Produktivität. Doch hinter der offiziellen Rhetorik verbirgt sich eine Annahme, die kaum hinterfragt wird: dass der grüne Wandel automatisch zu Wirtschaftswachstum und mehr Wohlstand führen wird. Aber stimmt das wirklich?
Eine englische Fassung dieses Textes finden Sie hier.
In Deutschland, das wieder einmal das Etikett „Kranker Mann Europas" tragen muss, kämpft Bundeskanzler Olaf Scholz vor der Wahl im Februar mit alarmierend niedrigen Vertrauenswerten. Aber vielleicht ist das gar nicht so überraschend. ****Die deutsche Industrieproduktion ist rückläufig, seit die grüne Agenda in Mode gekommen ist. ****Die energieintensive Produktion ist in nur wenigen Jahren um ganze 20 Prozent zurückgegangen. Volkswagen schließt Fabriken, Thyssenkrupp entlässt massiv Mitarbeiter und mehr als drei Millionen Rentner sind von Armut bedroht .
Wenn dies Europas „Mann auf dem Mond"-Moment ist, wie EU-Kommissarin von der Leyen ****es 2019 ausdrückte ****, dann ist das nicht viel, womit man angeben kann . Zumindest nicht, wenn man kein Sadist ist.
Der Bericht des ehemaligen EZB-Chefs Mario Draghi über die Wettbewerbsfähigkeit der EU wurde bereits früher diskutiert. Eines der Probleme, auf die hingewiesen wurde, war, dass europäische Unternehmen erheblich höhere Energiekosten haben als ihre amerikanischen Konkurrenten. Die Strompreise sind zwei- bis dreimal so hoch und die Erdgaspreise vier- bis fünfmal so hoch.
Deutschland ist vielleicht am schlimmsten dran, was zum Teil an der Entscheidung der ehemaligen Bundeskanzlerin Angela Merkel liegt, vollständig aus der Atomkraft auszusteigen (eine Entscheidung, die nicht nur keine breite Unterstützung fand , sondern die sie auch nicht als Fehler eingestehen will). Die Sabotage der Nord Stream 2 hat die Situation noch verschlimmert.
Ohne Realkapital kein wirtschaftlicher Wohlstand
Der Ausstieg aus der Atomenergie in Deutschland ist ein Beispiel dafür, wie politische Entscheidungen zur Verringerung der Kapazität der Wirtschaft beigetragen haben. Dasselbe gilt für die Sabotage der Nord Stream. Realkapital, wie Gebäude, Maschinen und Ausrüstung, ist für die Produktivität der Wirtschaft von entscheidender Bedeutung (z. B. Kennzahlen wie das BIP pro Arbeitsstunde). Ein größerer und effizienterer Kapitalstock ermöglicht die Herstellung von mehr Waren und Dienstleistungen mit der gleichen Menge an Arbeit, was zu mehr Produktion, höheren Löhnen und größerem materiellen Wohlstand führt. Das ist grundlegende Ökonomie. ****Wenn andererseits Realkapital aufgrund politischer Entscheidungen für obsolet erklärt wird, wie im Fall der Abschaltung der Atomkraft, verringert dies die Kapazität der Wirtschaft. ****Dasselbe gilt, wenn Realkapital zerstört wird, wie dies bei Nord Stream der Fall war.
Weiteres reales Betriebskapital wird zurückgestellt
EU-Kommissarin von der Leyen verspricht Besserung. Sie scheint überzeugt, dass der Niedergang der EU durch eine Verdreifachung der grünen Ziele des Blocks umgekehrt werden kann, und hat die Dekarbonisierung als eine der drei wichtigsten Säulen eines neuen „Wettbewerbsfähigkeitskompasses" aufgeführt. Wenn die Realität nicht den Erwartungen entspricht, kann man immer noch „Strg+Alt+Slogan" drücken und hoffen, dass niemand merkt, dass sich nichts verbessert hat.
Ihre Pläne bedeuten jedoch, dass bestehendes und derzeit funktionierendes Realkapital in Zukunft in noch größerem Umfang abgeschrieben wird. Dies lässt sich mit einer Nation vergleichen, die Jahr für Jahr ihre Naturschutzgebiete schrittweise erweitert. Tatsächlich geschieht dies auch. Der Kunming-Montreal-Rahmen für die Artenvielfalt sieht vor, dass bis 2030 30 % aller Flächen an Land und im Meer geschützt werden müssen. Ein Land, das derzeit weniger schützt, muss daher zusätzliche Gebiete identifizieren, die geschützt werden können. ****Der Prozess, 30 % aller Flächen zu schützen, wird wahrscheinlich das Produktionspotenzial der Wirtschaft verringern. ****Mit schrumpfenden Feldern wird es weniger Karotten geben (es sei denn, es werden bedeutende technologische Fortschritte erzielt).
Konsequenzen für Sicherheitspolitik und -vorsorge
Auf dem derzeitigen Weg wird mehr Realkapital auf die lange Bank geschoben, was weitreichende Folgen haben kann, nicht zuletzt für unsere Sicherheitspolitik. Wenn Russland beispielsweise Artilleriegeschosse etwa dreimal schneller produzieren kann, und zwar zu Kosten, die etwa ein Viertel der Kosten betragen, die die westlichen Verbündeten der Ukraine dafür aufbringen , dann ist klar, dass dies sicherheitspolitische Konsequenzen hat. Ebenso wird es negative sicherheitspolitische Konsequenzen haben, wenn die Strompreise in Deutschland fünfmal höher sind als in China, was derzeit der Fall ist . Im Vergleich zur EU hat China tatsächlich einen höheren Kohlendioxidausstoß pro Kopf, wobei der Unterschied den ****verfügbaren Daten zufolge etwa 50 % beträgt ****. Bereinigt um den internationalen Handel emittiert China pro Kopf 10 % mehr als Schweden .
Auch eine Perspektive der Vorsorge ist zu finden. Anfang der 1990er Jahre produzierten schwedische Landwirte fast 75 % der Nahrungsmittel des Landes. Heute ist Schwedens Bevölkerung deutlich gewachsen, aber die Nahrungsmittelproduktion hat nicht Schritt gehalten. Jeder zweite Bissen wird heute importiert. In Schweden können wir uns sogar rühmen, dass wir uns nicht einmal mit der einfachsten aller Feldfrüchte versorgen können -- Kartoffeln . Können wir wirklich sicher sein, dass deutlich erweiterte Naturschutzgebiete, wie sie im Kunming-Montreal-Rahmenwerk für Schweden vorgeschrieben sind, unsere Nahrungsmittelvorsorge nicht noch weiter verschlechtern werden?
Erinnert an kleine Gnome
Ich erinnere mich an eine Folge der 90er-Jahre-Serie South Park, in der kleine Gnome Unterhosen sammeln . Als sie nach ihrem Plan gefragt wurden, beschrieben sie ihre Methode:
- Unterhosen sammeln
- ???
- profitieren!
Übersetzt auf die grüne **Energiewende **:
- reales Kapital zerstören und Land und Meer erhalten
- ???
- wirtschaftlicher Wohlstand!
Was kann sich die EU wirklich leisten?
In der Wirtschaft geht es im Grunde um die Verwaltung knapper Ressourcen, was viele Menschen offenbar vergessen haben. Es ist höchste Zeit, zu hinterfragen, was sich die EU wirklich leisten kann. Können wir es uns wirklich leisten, uns für einen Krieg gegen Russland, China und den Iran zu rüsten und uns gleichzeitig mit grünen Versprechen von reduzierten Kohlendioxidemissionen und erhöhter Artenvielfalt selbst die Hände zu binden? Und das in einer Situation, in der die nächste US-Regierung wahrscheinlich massiv in die Steigerung ihrer Wettbewerbsvorteile durch Deregulierung, niedrigere Energiepreise, Steuersenkungen und einen Rückzug aus dem Pariser Abkommen investieren wird ?
Als von der Leyen für das deutsche Militär verantwortlich war, sei die Lage " katastrophal " gewesen. Alle sechs U-Boote des Landes waren außer Gefecht gesetzt . Zeitweise war kein einziges der 14 Transportflugzeuge des Landes flugfähig. Bei Übungen mussten deutsche Soldaten Besen statt Gewehren verwenden .
Hoffentlich wird von der Leyen in ihrem Umgang mit der Wirtschaft, der Verteidigung und der Abwehrbereitschaft der EU mehr Erfolg zeigen als in ihrer Rolle als deutsche Verteidigungsministerin. Es könnte jedoch auch an der Zeit sein, dass mehr Menschen die vorherrschenden Narrative, die unsere Politik prägen, in Frage stellen. Was, wenn die Fakten nicht ganz mit der Wahrheit übereinstimmen, die uns erzählt wird?
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28On "zk-rollups" applied to Bitcoin
ZK rollups make no sense in bitcoin because there is no "cheap calldata". all data is already ~~cheap~~ expensive calldata.
There could be an onchain zk verification that allows succinct signatures maybe, but never a rollup.
What happens is: you can have one UTXO that contains multiple balances on it and in each transaction you can recreate that UTXOs but alter its state using a zk to compress all internal transactions that took place.
The blockchain must be aware of all these new things, so it is in no way "L2".
And you must have an entity responsible for that UTXO and for conjuring the state changes and zk proofs.
But on bitcoin you also must keep the data necessary to rebuild the proofs somewhere else, I'm not sure how can the third party responsible for that UTXO ensure that happens.
I think such a construct is similar to a credit card corporation: one central party upon which everybody depends, zero interoperability with external entities, every vendor must have an account on each credit card company to be able to charge customers, therefore it is not clear that such a thing is more desirable than solutions that are truly open and interoperable like Lightning, which may have its defects but at least fosters a much better environment, bringing together different conflicting parties, custodians, anyone.
-
 @ e968e50b:db2a803a
2025-01-02 17:01:09
@ e968e50b:db2a803a
2025-01-02 17:01:09Hey all, anybody have a good file for a shroud to put an s9 into a duct? I just used this and this, which were advertised to muffle the sound, and actually just made it louder and created some resistance. I really want something like this, but they are only selling the product, not the file.
originally posted at https://stacker.news/items/833834
-
 @ 42342239:1d80db24
2024-12-22 08:38:02
@ 42342239:1d80db24
2024-12-22 08:38:02The EU's economy is facing a number of challenges, from high energy costs to low productivity. But behind the official rhetoric lies an assumption that is rarely questioned: that the green transition will automatically lead to economic growth and increased prosperity. But is this really true?
In Germany, which is once again forced to bear the label "Europe's sick man", Chancellor Olaf Scholz is struggling with alarmingly low confidence figures ahead of the election in February. But perhaps this is not so surprising. German industrial production has been trending downward since the green agenda became fashionable. Energy-intensive production has decreased by a full 20% in just a few years. Volkswagen is closing factories, Thyssenkrupp is massively laying off employees, and more than three million pensioners are at risk of poverty.
If this is Europe's "man on the moon" moment, as EU Commissioner von der Leyen expressed it in 2019, then it's not much to brag about. At least, not if you're not a sadist.
The former ECB chief Mario Draghi's report on the EU's competitiveness has been discussed previously in Affärsvärlden, among other things by the author and by Christian Sandström. One of the problems pointed out was that European companies have significantly higher energy costs than their American competitors, with electricity prices 2-3 times higher and natural gas prices 4-5 times higher.
Germany is perhaps worst off, thanks in part to former Chancellor Angela Merkel's decision to completely phase out nuclear power (a decision that not only lacked popular support but which she also refuses to acknowledge as a mistake). The sabotage of Nord Stream made the situation worse.
Without Real Capital, No Economic Prosperity
Germany's phasing out of nuclear power plants is an example of how political decisions have contributed to reducing the economy's capacity. The same applies to the sabotage of Nord Stream. Real capital, such as buildings, machinery, and equipment, is crucial for the economy's productivity (e.g., measures such as GDP per hour worked). A larger and more efficient capital stock enables the production of more goods and services with the same amount of labor, leading to greater production, higher wages, and increased material prosperity. This is basic economics. On the other hand, when real capital is declared obsolete due to political decisions, as in the case of the shutdown of nuclear power, it reduces the economy's capacity. The same applies when real capital is destroyed, as was the case with Nord Stream.
More Working Real Capital Will Be Put on the Back Burner
EU Commissioner von der Leyen promises improvement. She seems convinced that the EU's decline can be reversed by tripling down on the bloc's green goals, and listed decarbonization as one of three key pillars in a new "Competitiveness Compass". When reality does not live up to expectations, you can always press "Ctrl+Alt+Slogan" and hope that no one notices that nothing has improved.
However, her plans mean that existing and currently functioning real capital will be written off to an even greater extent in the future. This can be compared to a nation that gradually expands its nature reserves year after year. As it happens, this is also taking place. The Kunming-Montreal framework for biodiversity means that 30% of all areas, on land and at sea, must be protected by 2030. A country that currently conserves less than that must therefore identify additional areas that can be protected. The process of protecting 30% of all areas will likely reduce the economy's productive potential. With shrinking fields, there will be fewer carrots (unless significant technological progress is made).
Security Policy and Preparedness Consequences
On the current path, more real capital will be put on the back burner, which can have far-reaching consequences, not least for our security policy. For example, if Russia can produce artillery shells about three times faster, at a cost that is roughly a quarter of what it costs Ukraine's Western allies, then it's clear that this has security policy consequences. Similarly, if electricity prices in Germany are five times higher than in China, which is currently the case, then this will also have negative security policy consequences. Compared to the EU, China actually has a higher carbon dioxide emission level per capita, with a difference of about 50% according to available data. Adjusted for international trade, China emits 10% more than Sweden per capita.
A preparedness perspective can also be found. In the early 1990s, Swedish farmers produced nearly 75% of the country's food. Today, Sweden's population has increased significantly, but food production has not kept pace. Every other bite is imported today. In Sweden, we can even boast that we cannot even provide for ourselves with the simplest of crops - potatoes. Can we really be sure that significantly expanded nature reserves, as prescribed by the Kunming-Montreal framework for Sweden, will not further deteriorate our food preparedness?
Reminds One of Little Gnomes
I am reminded of an episode from the 90s TV series South Park, where little gnomes collect underpants. When asked about their plan, they described their method:
- collect underpants
- ???
- profit!
Translated to the green transition (the German Energiewende):
- destroy real capital and conserve land and sea
- ???
- economic prosperity!
What Can the EU Really Afford?
Economics is fundamentally about managing scarce resources, which many people seem to have forgotten. It's high time to question what the EU can really afford. Can we really afford to arm ourselves for war against Russia, China, and Iran while at the same time tying our own hands with green promises of reduced carbon dioxide emissions and increased biodiversity? This in a situation where the next US administration is likely to invest heavily in increasing its competitive advantages through deregulation, lower energy prices, tax cuts, and a withdrawal from the Paris Agreement?
When von der Leyen was responsible for the German military, the situation became "catastrophic". All six of the country's submarines were out of commission. At times, not a single one of the country's 14 transport aircraft could fly. German soldiers had to use broomsticks instead of guns during exercises.
Hopefully, von der Leyen will show more success in her handling of the EU's economy, defense, and preparedness than she has shown in her role as German Defense Minister. However, it may also be time for more people to challenge the prevailing narratives that shape our policies. What if the facts don't quite add up to the truth we're being told?
-
 @ 5391098c:74403a0e
2025-01-02 16:50:29
@ 5391098c:74403a0e
2025-01-02 16:50:29Ensaio em Prosa sobre Fotografia Analógica
Tenho especial fascínio pela fotografia analógica. É que se trata dum processo artístico muito mais complexo que a fotografia digital, devemos entender todos os aspectos da fotografia para obter o resultado pretendido, desde aspectos mecânicos da câmera como abertura e tempo do obturador, foco, iluminação, até a sensibilidade do filme utilizado e o resultado, quando alcançado, é verdadeira obra de arte pintada, onde a tela é a película química.
Importante dizer que meu fascínio pela fotografia analógica não me impede de reconhecer a importância da fotografia digital, não fosse essa você não estaria vendo minhas obras de arte que foram digitalizadas…
Da mesma forma que meu fascínio pela máquina de escrever não me impede de ter essa e outras páginas na internet. Parte do meu livro FILOSOFIA FUNDAMENTAL foi escrito graças a inspiração da máquina de escrever, como ocorreu no capítulo sobre o que seria evolução, escrevi integralmente na minha Olivetti Studio 46, pois havia faltado luz: o que me fez refletir sobre se o computador realmente é a evolução da máquina de escrever.
Outro exemplo foi a inspiração que as lindas formas arredondas de minha máquina de escrever da marca Érika me proporcionou, acabou resultando numa bela performance a qual dei nome de Paixão Erótika.
Por isso, acredito que os equipamentos analógicos não ofuscam nossa criatividade e na fotografia não poderia deixar de ser diferente.
No conjunto de fotografias analógicas abaixo utilizei uma Canon T50, objetiva de 50mm e filme Kodak Pro Image 100, a qual se encontra auto-fotografada em espelho, vamos ver:
Na foto abaixo utilizei luz amarela indireta da direita superior para esquerda inferior, o desfoque ao redor foi proposital com o objetivo de parecer estar olhando o mundo através das lentes da câmera, nesse caso ela estava olhando para sí mesmo. Mesmo estando a parede e o espelho no mesmo plano, a profundidade de campo do espelho é diferente, por isso esse efeito foi possível. Destaque especial para o “olho” do diafragma, deve ter aberto até f5.6, pois a luz não era muito forte. Se a luz fosse mais forte o diafragma teria aberto o mínimo f16 o que aumentaria a profundidade de campo impedindo o desfoque pretendido. O resultado foi alcançado, ao mesmo tempo que a câmera aparece, essa fotografia transmite essa mensagem subliminar:
https://image.nostr.build/a7cbfbe68a4bb89ae731c360c373ac8eff7599a5a100d13035eb234b5d788626.jpg
PERFORMANCE
Performance é o nome dado à mescla de mais de uma linguagem artística (arte visual, música, teatro, etc.) clicando em https://davipinheiro.com/id/performance/ você pode ver todas minhas performances. Nos exemplos abaixo a mescla se deu pela mistura de artes visuais criadas por mim e captadas pela fotografia analógica, vamos ver:
A foto abaixo se trata dum terrário que criei num tronco de árvore, arte plástica. Para fotografar utilizei luz amarela superior, o desfoque foi para destacar o objeto, especial destaque para o reflexo da luz no vidro para dar noção tridimensional de algo transparente:
https://image.nostr.build/e8026f9e99fa16631959954f8bb925af6f1764911f0a315ab0125bb413e3e89b.jpg
Na foto abaixo o mesmo processo da foto anterior, também utilizando uma Canon T50 com filme Kodak Pro Image 100 e objetiva de 50mm, diferenciando o enquadramento e a luz direta frontal:
https://image.nostr.build/4c44a0baf2b5ddaf63f83420952ab1b2e84f7df292f8e413a65f8134a2e7db58.jpg
A foto abaixo retrata o processo de criação da obra. Ironicamente, nessa foto, meu galo Cara de Palhaço mesmo desfocado no fundo se destacou, parecendo estar em pé no tronco:
https://image.nostr.build/d0d5e73ecbcdefa79ffd858d0143f41915c9deab7864d271d5ee724b3927f9bc.jpg
A foto abaixo se trata do pisca-alerta original da minha super DT200R (viva os motores 2 tempos!) que caiu depois de uma trilha kkk. A Ideia nesta fotografia era fazer o sol parecer estar acendendo o alerta que deveria aparentar estar flutuando no céu. Infelizmente não fui bem sucedido, pois os fios que penduravam o objeto acabaram aparecendo. É impressionante a capacidade de cálculo da Canon T50 e a velocidade do seu obturador, a nitidez da objetiva e a resolução do filme Kodak Pro Image 100, cujo conjunto conseguiu captar até os pequenos fios de nylon transparentes. Eu imaginei que a foto ia estourar e os fios não apareceriam, ledo engano. Pelo menos o enquadramento ficou correto: objeto um pouco mais acima do centro para dar sensação de altitude e levemente de perfil para dar noção 3d. Quem sabe com uma câmera que seja possível ajustar a velocidade do obturador eu seja bem sucedido…
https://image.nostr.build/808243d34b6dbeade25d38189163f9d58f6a12da9d00df17c85651d501e1bed8.jpg
A foto abaixo se trata da minha performance favorita com a fotografia analógica, pois fotografei o primeiro quadro que pintei, o qual dei o nome de Elipsoíris sendo ele posteriormente capa do meu livro FILOSOFIA FUNDAMENTAL, então aí temos três linguagens artísticas profundas na mesma performance: O quadro que virou livro fotografado analogicamente. A ideia desta performance foi enquadrar o quadro desfocado, o qual somente pode ser desvendado com os olhos certos, por isso a lente. Utilizei luz natural e uma lente velha de óculos. Especial destaque para os dois pontos de luz que refletiram na lente parecendo dois olhos, isso não foi planejado e deu um toque especial para a fotografia, cabendo diversas interpretações, esse é o objeto da arte em geral. Fiquei muuuito contente com o resultado:
https://image.nostr.build/6bb5b802b3ad1bb7262b925225fcfb0b8b00654fa0fec240be57f648c32245af.jpg
Já na fotografia analógica abaixo considero uma performance porque não se trata duma fotografia comum de paisagem, flores, arquitetura, animais ou pessoas, visa passar uma mensagem. Utilizando apenas a luz natural, regulei o foco da Canon T50 para as lentes dos meus próprios óculos e escolhi um dia especialmente nublado e escuro para simbolizar as dificuldades pelas quais todos passamos no dia-a-dia, quando acreditamos por algum momento que as luzes estão apagadas para nós, até que com os óculos certos podemos enxergar com maior nitidez o horizonte, os óculos podem ser a palavra de Deus ou qualquer outra coisa que te ilumine e esclareça. Com certeza essa fotografia terá um bom uso em meus próximos escritos:
https://image.nostr.build/b44b573bb39cdf5f2eb446e818bbf59d5dab9d3815ac6e917440b2f6b1ff431c.jpg
DUPLA EXPOSIÇÃO
Eis aqui um recurso nato da fotografia analógica: a dupla exposição. Se trata de fotografar mais de uma vez em cima do mesmo filme de modo que as imagens se sobreponham. Como esse método podemos simular movimento numa única fotografia, fazer montagens de disco voador kkkk, enfim a imaginação é o limite, vamos ver:
Nessa fotografia analógica abaixo ocorreu uma quádrupla exposição, pois cliquei quatro enquadramentos diferentes sob o mesmo filme. Foi especialmente difícil fazer porque a Canon T50 não tem esse recurso, então tive que enganá-la pressionando o botão de rebobinar o filme ao mesmo tempo que disparava a câmera. Como eu estava usando o filme Kodak Pro Image que possui asa 100, também regulei a máquina como se estivesse usando um filme asa 25, então sabia que podia disparar quatro vezes sem queimar o filme. Pedi para a modelo (minha Mãe, kkk) ficar em três posições diferentes dando a impressão de movimento e não satisfeito no final ainda fotografei o sol. Adorei essa foto:
https://image.nostr.build/5f8e2962e2ee94259d4dd5d3b777976a4d20ba293a5a4e68e81e30a0e1975543.jpg
FOTOS EM MACRO OU CLOSE
Acredito ser possível obter uma fotografia analógica em macro mesmo sem lente especial, tudo depende da pecinha que fica atrás da câmera: você, kkkk. Devemos tentar, se não obtivermos uma fotografia em macro, ao menos um close teremos, vamos ver:
Na foto abaixo há um minúsculo cogumelo que cresceu num barranco qualquer, apareceu nitidamente no negativo, mesmo sem uso de lupa, por isso considero um macro, na verdade é apenas uma foto divertida:
https://image.nostr.build/02aa4bbdc0cf54519b694c75237693fc2a6569fe4f3167220b05c7498757b822.jpg
Já a foto abaixo é apenas um close, o ninho é especialmente profundo, por isso o leve desfoque nos ovos: para dar noção de profundidade. O foco dos quatro cantos da caixa está bem ajustada para dar noção tridimensional do objeto:
https://image.nostr.build/24e5dcdd0e5a3560b341fe4f0d0d93b7d562f2d58054ac308a8e312c2707100c.jpg
O PRIMEIRO QUADRO DO ROLO
Na fotografia analógica cada rolo de filme nos dá pelo menos um tipo de fotografia artística bem específica. Se trata do primeiro quadro do rolo, onde ocorre uma parcial sobre-exposição. Isso se deve a incidência da luz diretamente no filme quando estamos carregando a máquina com o filme. A maioria das máquinas analógicas somente começa a contar os fotogramas após alguns disparos para evitar isso. Cabe ao fotógrafo saber aproveitar os fotogramas existentes antes do número 1, enquadrando a cena normalmente e disparando antes do número 1. Os resultados são quase imprevisíveis e geralmente interessantes.
Abaixo uma fotografia analógica fantástica porque quase sempre a sobre-exposição do primeiro quadro do rolo ocorre nas extremidades da foto e nessa aí ocorreu no meio. Para conseguir esse efeito carreguei a máquina no escuro e acendi a luz no exato momento que estava fechando a tampa da câmera. Por uma fração de segundo o primeiro quadro do rolo foi exposto parcialmente a luz, sabia que iria ter uma fotografia diferente, jamais imaginei que a sobre-exposição iria sair no meio do fotograma, muito curioso:
https://image.nostr.build/a2e08aab686af64df949e83b4ff3b0a00952698a7a138412f7753ebc0dd63d1f.jpg
Na fotografia abaixo repeti o mesmo processo anterior. Como o tempo entre acender a luz e fechar da máquina foi diferente a sobre-exposição ficou bem visível na extremidade da foto. Especial destaque para sua incidência no lado direito, quando deveria incidir no lado esquerdo, pois na Canon T50 o filme roda da esquerda para direita. Essa aparente inversão de lados se deu porque fotografei com a máquina de cabeça para baixo:
https://image.nostr.build/270681be8de71b6c833507dda6bfe4b5233c9b871aa97ea8fc2ebdcdd46a682a.jpg
FOTOS DE AÇÃO
Registrar uma ação com fotografia analógica é especialmente difícil se a máquina não calcula a abertura e tempo de exposição automaticamente, porque tudo acontece muito rápido e você não tem tempo de ficar pensando. Felizmente a Canon T50 é muito boa para esse tipo de fotografia, tive que me preocupar apenas com o foco. O que essa máquina me fez suar para fazer as duplas exposições acima, tirou de letra esse memorável momento, vamos ver:
Na foto abaixo quando avistei esse grupo de corajosos saltando de paraglider corri pedir autorização para fotografá-los e rapidamente carreguei a máquina. Comecei a fotografar mesmo antes da máquina registrar o primeiro fotograma do rolo, tendo obtido esse lindo efeito de sobre-exposição de primeiro quadro do rolo:
https://image.nostr.build/8e32e22d3bf7c897d7111e85555146e38bb139985c50b2795fe809b31880c7d8.jpg
Já a foto abaixo foi a terceira do rolo. Tomei o cuidado de enquadrar tanto a alçada de vôo do paraglider quanto essa linda Veraneio, o que descreve em uma única foto o espírito aventureiro do pessoal. Reparem no sol refletindo sobre as nuvens, que lindo tudo:
https://image.nostr.build/5bf0444e4621406d858ab70725c1ee2f6a7e39b87663e23a18085a32b9a06f6a.jpg
Na foto abaixo tive que registrar mais uma dessa linda Veraneio, sou apaixonado por motores e mecânica, ela quase roubou a cena kkkk. Especial destaque para o detalhe do carro e da câmera que a fotografou serem da mesma época, sensível retorno ao passado. Verdadeira máquina do tempo essa foto. Se eu não dissesse que esta foto foi tirada no final do ano de 2020 daria para dizer que foi uma foto tirada de uma Veraneio Zero Km da época, segredinho nosso, kkk.
https://image.nostr.build/f5284ff30986ad84d22f137e0a330067f91564907da8acf04c9eb93a991cbcf2.jpg
Na foto abaixo voltando à cena, agora do Ângulo certo kkk. Esse foi a segunda foto, perceba ainda a presença do efeito de sobre-exposição do primeiro quadro. Aqui a máquina estava marcando o primeiro fotograma, tadinha kkk
https://image.nostr.build/5c1d73f7d802fd1f730427e29f921c82e410c5dce3112a3133d6fce294d310c6.jpg
Na foto abaixo a luz estava perfeita, o sol iluminava atrás de mim, incidindo frontalmente para o enquadramento da foto, linda essa:
https://image.nostr.build/156fc878dd18257ad1f59d1b5d3fd719c7e773937356fad6ea09b0ce1f151f12.jpg
Paraglider quase em posição de vôo, a foto ficou quase perfeita porque o momento em tela era a Hora de Ouro, momento do entardecer quando a posição do sol deixa o céu dourado, fenômeno muito querido pelos fotógrafos analógicos; até pelos digitais também. Mesmo assim eu não estava satisfeito, queria fotografar mais de perto. Dei zoom correndo para frente e o resultado você vê abaixo:
https://image.nostr.build/b1f610695bd57db8abe7408df318978b6e69e85fe620a589b12fb9bcaae66156.jpg
Abaixo a fotografia analógica simplesmente perfeita, sol na posição certa, hora de ouro, perfeito enquadramento e foco, tudo certo, universo conspirando à favor… ganhei o dia sem saber. Só descobri depois que revelei. O chão não foi cortado é que o piloto do paraglider já estava no desnível do chão pronto para saltar:
https://image.nostr.build/93a7e416d11c996b65a32b019667a43124d96985109d34fd1a9b239ef365bbfe.jpg
Abaixo O salto… tive que correr para o barranco para dar zoom, outra foto perfeita na hora de ouro:
https://image.nostr.build/f254c2e71863a233816b517564dd5fb7fe85ee0bd927b02687fba43bde53dcd6.jpg
FOTOGRAFIA ANALÓGICA DE ANIMAIS
É especialmente difícil fazer um animal posar para gente, temos que ter um pouco de comida pra negociar kkk. Não fosse a Canon T50 calcular a exposição sozinha seria ainda mais difícil porque os momentos são muito rápidos e você não tem tempo para regular a abertura e tempo de exposição, tive que regular apenas o foco. Mais um ponto para essa notável máquina que me fez apanhar na dupla exposição acima. A fotografia analógica de animais também é um tipo de fotografia de ação, temos que ser rápidos no gatilho, vamos ver os resultados:
Abaixo novamente dei zoom chegando bem perto, fotógrafo de verdade não tem medo, tudo pela arte!
https://image.nostr.build/5f0af116b1fd81edb3f21dfd5d7cce6c534751ac8660bd5fb58ce08c652d8aaf.jpg
Abaixo foco no segundo plano, acabei pegando os dois de perfil:
https://image.nostr.build/fbd78fcf71749569444d3438e0d5283d321fc3f3350cacc6e4a3e9a0cdc914f5.jpg
Abaixo foco no segundo plano. Aqui peguei os dois olhando para mim e dizendo xiiiis, kkk.
https://image.nostr.build/3a1f50ee1e3c6213b337654e69ee23819ab60100c8a1a049ee0b2b66fac0d8f8.jpg
Abaixo podemos comprovar que o fotômetro da Canon T50 é matricial e não pontual, porque o centro da foto tinha muito mais luz que os cantos:
https://image.nostr.build/11a8a5a7ff14a661755f04f743d70d3dd1a9d11e412791ce42f5cbf1da1c6be2.jpg
Abaixo linda foto: Cavalo da Montanha. Eu estava esperando a Hora de Ouro chegar, pena que quando chegou o modelo não quis mais ser fotografado kkk.
https://image.nostr.build/83429975966cb4b0e71e5e089651d4585513d823fea404014b0b78b21e859302.jpg
Abaixo lindo close de perfil com fundo totalmente desfocado. Preto absoluto, a fotometria esta certinha:
https://image.nostr.build/f36aed8fa89b6ba81dd77c7d3b32c24424483e626a9634cbadb16baf91427d66.jpg
Abaixo muita coisa acontecendo ao mesmo tempo: As galinhas comendo, o milho sendo jogado, a sombra do fotógrafo… Para obter essa foto joguei o milho para o alto e tive que ser tão rápido no gatilho quanto o Kid Morengueira. Você pode perceber na minha sombra que estou segurando apenas a câmera, o pote de milho já tinha voado longe kkk. Escolhi especialmente um dia ensolarado para que o fotômetro da Canon T50 usasse toda a velocidade possível no obturador, sendo possível congelar o milho no ar sem muito efeito borrão.
https://image.nostr.build/d566e46a8a3cba8855e80295910e5addb0a8aa7735093c9f93f129cac2379472.jpg
Abaixo galinha chocando numa roda de carro. Como amo animais e carros, para montar essa cena tive que forrar uma roda velha de carro para formar um ninho e esperar, esperar e esperar… No momento certo a Jurema se sentiu confiante para entrar na roda. Nem se incomodou com minha presença pois estava de papo cheio, pois é, também tive que negociar com a galinha, isso é a fotografia analógica de animais kkk. Percebam novamente que o fotômetro da Canon T50 é matricial, pois a maior parte da foto era com pouca luz e o raio de sol que entrava estourou a foto. Percebam ainda como eu estava perto da galinha, pois foquei em sua cabeça e o resto do corpo que estava um pouco mais distante saiu desfocado. Certamente a câmera estava com abertura máxima f1.8 e com uma velocidade bem lenta, o que explica a baixa profundidade de campo. Além disso se a Jurema tivesse mexido a cabeça na hora do disparo certamente teria saído um borrão por causa da baixa velocidade. Acabou saindo tudo certo e meus dias de espera por essa foto não foram em vão.
https://image.nostr.build/d7484609c8ff9be05ee6d518def402f66484a02109dc96ef5c734b11216385bf.jpg
FOTOGRAFIA ANALÓGICA DE ARQUITETURA
Na fotografia analógica de arquitetura devemos conhecer os conceitos básicos de iluminação e preenchimento, trabalhamos apenas com luz natural e deve ser bem usada para termos a noção tridimensional da construção. Conforme ensina Fernando Bagnola, a tridimensionalidade do objeto depende da incidência da luz em três pontos diferentes e com intensidades diferentes, algo difícil de se obter apenas com a luz do sol, vamos ver:
Abaixo se trata do Museu do Olho em Curitiba/PR. Como sua parte frontal é escura e o sol se posicionava atrás da construção tive de me posicional na sua lateral, assim consegui obter um resultado tridimensional, pois o sol iluminava a parte de cima, refletia na parte de baixo em menor intensidade e na parte frontal quase não havia luz. Se eu estivesse posicionando na frente da construção o efeito tridimensional seria impossível:
https://image.nostr.build/6f74c1c7e606f7950eaf45007868b92e9a0288722b3d5e580ecaa4930700e3ea.jpg
Abaixo para minha sorte, nesse exato momento um grupo de jovens contracultura (assim como eu) passavam pelo local, tornando a foto icônica pela presença de jovens modernos contracultura contrastando com arquitetura moderna da cultura tradicional. Minha posição em relação ao sol também favoreceu o sucesso desta fotografia, tendo iluminado corretamente todos os pontos de interesse:
https://image.nostr.build/7c374205d7df21985a6a71c6c17e4f67ab29baf452f0cd406b869df94d68296c.jpg
Abaixo esse aqui é um exemplo de fotografia analógica arquitetônica errada. O enquadramento foi frontal em razão do desejo de captar o reflexo dos edifícios nos vidros negros do “olho”:
https://image.nostr.build/f9a0869a165bc7e634944c01e59085203347ab6c353610bdcaace30ee3ed8d8a.jpg
Abaixo se trata do Panteon dos Heroes na Lapa/PR um monumento erguido para guardar os corpos dos soldados das forças republicanas que pereceram durante o chamado Cerco da Lapa, batalha da Revolução Federalista de 1894. Aqui o dia estava nublado, momento perfeito para fotografar uma arquitetura tão triste como essa. Não me importei com a questão tridimensional, pois era impossível, não havia sol. Quis retratar a tristeza na foto. O filme usado foi o mesmo (Kodak Pro Image 100). Aqui percebemos que a química desse filme é ajustada para a luz amarela do sol como branco absoluto, como o céu estava nublado, a luz natural estava com temperatura mais fria o que puxou o tom mais para o azul e o roxeado da foto devem ter sido os raios ultravioleta. Se eu estivesse usando um filtro ultravioleta provavelmente a foto sairia mais acinzentada. Me recordo que nesse dia estava tudo cinza. De qualquer forma adorei esse tom arroxeado da foto. Fica a dica: conseguimos o mesmo efeito de um filme Lomochrome Purple caríssimo com um filme baratinho, basta fotografar nessas condições:
https://image.nostr.build/24f91369c12e83861f7eec38ff99f1869f08ae1eec06c798ccbe08af62263a2e.jpg
Abaixo novamente o tom arrocheado com um filme barato. Para se ter uma ideia um Lomochrome Purple costuma custar seis vezes ou mais que um que o Kodak Pro Image 100 de R$ 30,00 à R$ 40,00 na data da publicação deste artigo em 09/04/21. Percebam que no momento desta foto as nuvens deram uma trégua e alguns raios de sol passaram dando uma leve noção tridimensional da arquitetura. O certo seria eu estar um pouco mais à esquerda para aproveitar bem a iluminação. Mesmo assim, me senti feliz com a triste foto kkk pois mesmo com a luz amarela do sol refletindo o efeito Lomo-Violeta ocorreu:
https://image.nostr.build/099a1a4d7857325e59f5b35805c0ebb5c3fa55af45de2096236f1dfbadca4d4a.jpg
Abaixo parece que a foto está mal enquadrada. E está mesmo. É que no lado direito havia um poste de energia elétrica muito feio, eu não queria que aparecesse. Me preocupei apenas com a iluminação e obtive sucesso com a noção de profundidade da arquitetura. A foto está puxando para o amarelo porque a Universidade Federal do Paraná em Curitiba é meio amarela mesmo.
https://image.nostr.build/48a4d517488fc1656e027568ad314688bc0fd9995e67289003f832eb904e5260.jpg
Abaixo para finalizar o conjunto de fotografias analógicas arquitetônicas nada melhor que um cemitério, afinal todos vamos morrer um dia, devemos sempre lembrar disso para fazer nossas vidas mundanas valerem a pena. Quando morremos não levamos nada a não ser nossas experiências evolucionais, nossas graças e pecados. Devemos deixar um legado, algo positivo para quem fica. Pois bem, foi nesse contexto a foto. Para mim a morte deve ser evitada. Quando ocorrer, se fizermos tudo certo vamos para luz, as trevas são aqui na terra mesmo. Portanto, ao contrário da maioria dos fotógrafos, escolhi um dia ensolarado para fotografar ali. Quis simbolizar a luz que nos aguarda após a morte. Então me posicionei dentro do cemitério para fotografar de dentro para fora. Esperei o sol se posicionar de forma que dos portões para fora houvesse pouca luz, tal como é o mundo, deixando toda a iluminação para dentro dos portões. Percebam como pequenos detalhes fazem toda a diferença numa fotografia analógica artística. Essa foto pode perfeitamente ser usada para ilustrar qualquer material que corrobore com esse pensamento. Se eu quisesse retratar que a vida é mil maravilhas e a morte um triste fim, deveria estar do lado de fora dos portões com tudo iluminado exceto o interior do cemitério. Interessante não…
https://image.nostr.build/051592db1d3612c719621547a69bc8dfd0319d6b89656451d5b60582ae864e8e.jpg
FOTOGRAFIA ANALÓGICA DE PESSOAS
Basicamente se divide em dois tipos, a cena e o retrato. Na cena a pessoa posa para a foto sem contudo revelar sua personalidade, é uma cena criada artificialmente. Já o retrato, no conceito artístico da fotografia, ocorre quando conseguimos captar o interior da pessoa. Por exemplo: se for uma pessoa triste ela aparecerá com semblante triste, se for uma pessoa alegre com semblante alegre, não necessariamente sorrido. Se for uma pessoa sofrida suas rugas, desasseios e receios ficarão visíveis. Se for uma pessoa engraçada sentiremos vontade de rir ao ver seu retrato. O retrato é algo verdadeiro e espontâneo da pessoa. Se uma pessoa triste aparece sorrido não é um retrato e sim uma cena, vamos ver:
Abaixo normalmente na fotografia analógica de pessoas o correto é deixar o segundo plano mais escuro e o primeiro plano mais claro. Ai quis fazer diferente. Pedi para o modelo (Meu Melhor Amigo) se posicionar de costas para o sol, pois já tinha avistado aquele arco-íris no fundo. Nesse caso foi um retrato pois meu amigo apareceu sorrindo sem eu pedir e sei que ele é uma pessoa feliz e engraçada, pois vive contando piadas e seu repertório é infinito. O interessante é que esse não é um retrato comum e sim um retrato artístico, pois inverti a iluminação dos planos e ainda captei uma arco-íris, foi uma cena construida para um retrato, ideia antagônica para fotografia analógica de pessoas. Como resultado obtive uma fotografia que parece uma montagem, onde a imagem do modelo ter-se-ia sido colada sobre a paisagem, tamanha foi a diferença de iluminação entre o primeiro e segundo plano. Contudo, um pequeno raio de sol que incidiu sobre o canteiro inferior esquerdo não me deixa mentir que a fotografia é autêntica. Além disso tendo os negativos que não mentem kkk. Essa foi minha fotografia preferida de pessoas, pela qualidade do resultado artístico e pela pessoa do modelo, um abração amigo! Vou chamar essa foto de “Meu Parça na Praça”:
https://image.nostr.build/51db1df7741227dc2d86529bc9e7a93cf27365f0f2d7b591a4e84a9a05855dfb.jpg
Abaixo sou eu. Se trata apenas de uma cena simples porque minha expressão não aparece e sequer minhas roupas traduziam minha personalidade. Regulei o foco da máquina para 5 metros, entreguei-a para meu amigo e contei alguns passos para trás. Não me preocupei muito em acertar minha posição em exatos 5 metros porque o dia estava bem ensolarado e sabia qua a Canon T50 iria abrir pouco o diafragma por causa disso, o que aumentou a profundidade de campo consideravelmente. Podemos perceber no fundo a Universidade Federal do Paraná sem qualquer desfoque por causa disso. O maldito poste que tentei evitar na foto arquitetônica da UFPR acima acabou aparecendo aqui, mesmo assim gostei da foto pelo tom de cores que só a fotografia analógica nos dá.
https://image.nostr.build/ce8af555274333fa8a26375247373ca92315e87d7414bcc9ad7b5a4840cb3a21.jpg
FOTOGRAFIA ANELÓGICA DE OBJETOS
A fotografia analógica de objetos, assim como a arquitetônica, deve se obedecer os conceitos básicos de iluminação para obter noção tridimensional do objeto. Além disso, a cena montada deve combinar com o objeto para entrar em sintonia com o conceito natural de beleza, vamos ver:
Abaixo queria fotografar um objeto qualquer, então peguei essa faca. Esse objeto combina muito bem com o ambiente rústico do campo, então a finquei-a num toco de árvore com vista para o campo, tomando cuidado para ela ficar levemente torcida e dar a noção tridimensional. Naturalmente a foto ornou porque o objeto esta em sintonia com a cena. Essa deve ser a combinação da fotografia analógica de objetos, por exemplo. A não ser que o fotógrafo busque justamente causar repudia invertendo a combinação do objeto com a cena. Por exemplo: para causar nojo pode-se fotografar barro em formato de cocô num prato. Merda e comida são coisas totalmente opostas e essa inversão naturalmente é perturbadora para qualquer ser humano. Existe uma lógica natural de combinação de objetos com a cena. Enfim, podemos inclusive combinar mais de um objeto secundário para criar uma cena ao objeto principal, como veremos mais abaixo com a xícara de café:
https://image.nostr.build/6474901ce85d34aef3421ce5f720e258208c50aeb57e9893c8a750c6dc8fc1df.jpg
Na foto abaixo o objeto principal é uma caneca de café. Para criar a cena utilizei outros três objetos. O palheiro que combina com café, a tampa da objetiva da minha Canon T50 que combina com o efeito da cafeína para pensar mais rápido sobre as cenas que irei montar, e o vazo de suculenta que remete a algo mais áspero e amargo como o café e o palheiro. Se o objeto principal fosse um copo de milkshake no lugar do palheiro haveriam balas coloridas, no lugar da tampa da máquina haveria um guardanapo e no lugar da suculenta haveria um flor fofa e cor de rosa. Falando em flor vou encerrar este ensaio com o tópico sobre fotografia analógica de flores para deixar todos felizes no final:
https://image.nostr.build/8e95c6bae536cfea47e3c5d44aa63725ab8fe20eacd1c6d5eeaae1720dd0a9e5.jpg
FOTOGRAFIA ANELÓGICA DE FLORES
É um tipo de fotografia livre da fotografia analógica, sem muitas preocupações para o fotógrafo analógico, devemos atentar apenas para a vivacidade das cores e para isso o dia deve estar especialmente ensolarado. Se for fotografia interna de preferência usar luz quente (amarela), o resto é só diversão, vamos ver:
https://image.nostr.build/fc8cf663300794761b0d8dc6f1a765e3a423c65a4ad4a85a7885b00716b46533.jpg https://image.nostr.build/dc4fbe15a7b46817d66bdbeb3d0e11851999b2c1292c576fd457956436e75c77.jpg https://image.nostr.build/73fa3b1b30a088954b342294e1b0aa555a693c3ad425dea9807d2238ec529747.jpg
Viva a fotografia analógica!
Se você deseja fazer um ensaio artístico com fotografia analógia comigo entre em contato e terei o prazer de agendar o serviço.
-
 @ 07804b78:c375c543
2024-12-15 12:56:05
@ 07804b78:c375c543
2024-12-15 12:56:05Japanese follows. 日本語はあとで。
This article is for the 14th day of Nostr Advent Calendar 2024 (relay blogging). The article for the 13th day was "Open Sats 申請編" (Applying for Open Sats) by mono-san. The article for the 14th day will be "Nostrはじめました。" (I started Nostr) by bro-san.
Thinking of Thingstr
I've come up with an idea for Other Staff that I think is interesting (at least, for me), so I'm going to write about it. I actually wanted to show you the implementation and brag about it, but it's not solid enough to be implemented yet.
The key idea is just “add a reaction to the WikiData ID”.
WikiData
There is a service called WikiData. It is a knowledge base that provides structured data. You may be wondering what it is, but the important thing to understand here is that WikiData assigns identifiers to a fairly wide range of “objects” and “things”.
So, if you can react to this, you can think of various applications just by thinking of it for a moment, right?
For example, the anime series “There are too many losing heroines!” is assigned the ID
Q123819103. The corresponding page is https://www.wikidata.org/wiki/Q123819103 .(NOTE: The canonical URI for entities on Wikidata is http://www.wikidata.org/entity/Q1142841. This is in accordance with Semantic Web conventions, and is not https, but http. Also, this URI does not necessarily match the actual address of the correspnding web page. Just an identifier. In most cases, it will redirect).
What can wd do?
For example, what about a website that records your anime viewing history? You can record what you want to watch with 👀, what you've already watched with ✅, and your favorites with ☆. You can also express your “likes” for production companies, staff, voice actors, etc. In this way, you can see what a particular user likes.
This could be a movie, a book, a comic, an author, music, an idol group, a place, or food (Someone likes pork cutlet
Q1142841). The fact that you can record everything in the same framework is what makes it interesting.What form of event should it be recorded as?
There is probably room for discussion about how to record this information in a concrete way. The simplest way would be to use NIP-25's "Reactions to a website" kind:17 (a.k.a. Makibishi). How about something like this?
json [ ["i", "wd:Q123819103", "http://www.wikidata.org/entity/Q123819103"], ]Since NIP-73 has External Content IDs, it would be good if we could include WikiData here so that we could write
wd:Q123819103. Actually,isbn:and other identifiers have already been defined, so it is possible to use the current NIP range to describe books (however, the authors do not have IDs. If we use WikiData as an ID, we can also describe reactions related to the author). Of course, it is not a matter of choosing one or the other, and it is also fine to add the ISBN tag at the same time as the WikiData tag for books.Search for recorded reactions
So far, this is all very simple, but it would be inconvenient if we didn't include tags to mark subsets of reactions (for example, only those related to anime) so that we can query them together. When we try to create a site that is specialized for a certain purpose, we need to be able to extract the reactions that are necessary.
On Wikidata, the predicate
wdt:P31(instance of) is used to group together concepts that represent the same thing. For example, how about including this in theltag? "There are too many losing heroines!" is a "Japanese television anime series (Q63952888)", so:json [ ["i", "wd:Q1142841", "http://www.wikidata.org/entity/Q1142841"], ["l", "wdt:P31 wd:Q63952888"] ]UPDATE(2024-12-15): rnurachue-san suggested that
#lor#Lmight be better for labeling (the first version used#a). I think that's a good idea, so I've updated the article. nostr:nevent1qgswamu0rsela0kwhj87p24ueapxdp04vzz7ar0pp6lfyq923t3l02cqyr9786635s60ra0f973nwv2sln2l74lqx4twdlgxfz2jgevpvsgtc9zwn6dHowever, when you think about creating an anime website, you may want to query both TV anime and anime films. This makes things more complicated. "Japanese TV anime series (
Q63952888)" is a subclass (subclass of;wdt:P279) of "Anime series (Q117467261)", which is in turn a subclass of "Anime (Q1107)". However, if you were to embed this hierarchy in each reaction, it would waste a lot of space. The following query will get all the superclasses of "Japanese TV anime series (Q63952888)", but there are 54 of them.https://query.wikidata.org/#%23%20Subclass%20hierarchy%20traversal%20for%20Q63952888%0ASELECT%20%3Fitem%20%3FitemLabel%20%3Fsuperclass%20%3FsuperclassLabel%0AWHERE%20%7B%0A%20%20%23%20Starting%20class%0A%20%20wd%3AQ63952888%20wdt%3AP279%2a%20%3Fsuperclass%20.%0A%20%20BIND%28wd%3AQ63952888%20AS%20%3Fitem%29%0A%20%20SERVICE%20wikibase%3Alabel%20%7B%20bd%3AserviceParam%20wikibase%3Alanguage%20%22%5BAUTO_LANGUAGE%5D%2Cen%22.%20%7D%0A%7D%0AORDER%20BY%20%3Fsuperclass%0A
So, I think it should be okay for practical purposes to embed
P31s of the reaction target. In other words, if you search for "anime seriesQ63952888" and "anime movieQ20650540", that should be enough. Fortunately, the conditions for single-character tags work with OR, so you can query multiple tags at once. we'll have to try it to see how well it works in practice, though.Discussion: Which kind should I use?
So far we have considered using kind:17, but we have not yet decided whether it is a good idea to mix Thingstr events with reactions to web pages.
Also, there may be a debate over whether to record regular events or addressable events, depending on the purpose of use. For example, if you want to record the transition of viewing results and impressions on an anime viewing site, you should use regular events, and if you want to maintain the viewing status, you should use addressable events.
What do you think?
Other ideas
If we can react to Nodes on OpenStreetMap using the same framework, we might be able to create something like Swarm. Since the views you want to see will differ depending on the purpose, it would be good to create various sites while having a consistent way of recording. Wouldn't that be the most Nostr-like thing?
Summary
I discussed how to use WikiData and OpenStreetMap as an ID infrastructure and realize various check-in and review services with a unified data model by using them on Nostr. Please let us know if you have any feedback. Or why not try implementing it?
この記事は Nostr Advent Calendar 2024 の14日目の記事です。13日目の記事はmonoさんによる「Open Sats 申請編」でした。15日目の記事はbroさんによる「Nostrはじめました。」です。
Thingstrについて考えた
面白そうな(と勝手に思ってる) Other Staff のアイディアを思いついたので、書いてみます。 本当は実装を持ってきて自慢したかったのですが、まだふわっとしていて実装に落ちていません。
コアになるアイディアは「WikiData の ID に対して、Reactionをつける」これだけです。
WikiData
WikiData というサービスがあります。構造化データを提供する知識ベースです。 なにそれ?という感じですが、ここで大事なのはWikiDataはかなり広範な「もの」「こと」に識別子(Identifier)を付与している、ということです。
だから、これにリアクションできれば、ぱっと思いつくだけでもいろいろな応用ができそうじゃないですか。
例えば、アニメシリーズ「負けヒロインが多すぎる!」には
Q123819103というIDが振られています。これに対応するページとして https://www.wikidata.org/wiki/Q123819103 があります。(ただし、WikiData のエンティティに対する canonical な URI は http://www.wikidata.org/entity/Q1142841 であることには注意が必要です。セマンティックウェブの作法で https ではなく http になっています。そして、このURIは必ずしもWebページのアドレス一致しません。大抵の場合はリダイレクトされます)。
なにができるの
たとえば、アニメの視聴記録サイトはどうでしょう。👀は見たい作品、✅は視聴済み、☆はお気に入り、みたいに記録していく。制作会社、スタッフ、声優、...に対してLikeを表明したりできそうです。そうすると、あるユーザが何にLikeしているかわかります。
これが映画でもいいし、書籍、漫画、作家でもいいし、音楽でもいいし、アイドルグループでもいいし、場所でもいいし、食べ物でもいい(とんかつ
Q1142841が好き、とか)。全部同じ枠組みで記録できるのが面白そうなところです。どういうNostrイベントで記録する?
具体的な記録の仕方には議論の余地があるでしょう。一番単純なのは、NIP-25の "Reactions to a website" kind:17 (Makibishi) を使う方法でしょうか。こんなのはどうでしょう。
json [ ["i", "wd:Q123819103", "http://www.wikidata.org/entity/Q123819103"], ]NIP-73にExternal Content IDsがあるので、ここにWikiDataを入れられるようにして
wd:Q123819103と書けるとよさそうです。実はisbn:などはすでに定義されているので、書籍に関しては現行のNIPの範囲でもうまいことできます(ただ、著者にはIDが振られていません。WikiDataをIDに使うと著者に関するリアクションも記述できます)。もちろん、どちらか一方を選ぶというものでもなくて、書籍にはWikiDataのタグと当時にISBNのタグを付与しておいてもいいと思います。記録されたリアクションを検索する
ここまではシンプルでよいのですが、リアクションの部分集合(たとえばアニメに関連するものだけ、とか)をまとめてクエリできるように、目印となるタグを入れておかないと不便です。ある目的に特化したサイトを作ろうとしたとき、必要になるリアクションが抽出できるようにしておかないといけません。
WikiData では
wdt:P31(instance of) という述語で、ある概念が何を表しているかをグルーピングしてくれています。例えばこれをlタグとかに含めておくのはどうでしょうか。負けヒロインが多すぎる!は「日本のテレビアニメシリーズ(
Q63952888)」なので、json [ ["i", "wd:Q1142841", "http://www.wikidata.org/entity/Q1142841"], ["l", "wdt:P31 wd:Q63952888"] ]みたいな感じで付与します。
UPDATE(2024-12-15): rnurachueさんからラベル付けには
#lまたは#Lのほうがよいかもという提案をいただきました。最初のバージョンでは#aを使用していました。そのとおりだと思ったので更新しました。 nostr:nevent1qgswamu0rsela0kwhj87p24ueapxdp04vzz7ar0pp6lfyq923t3l02cqyr9786635s60ra0f973nwv2sln2l74lqx4twdlgxfz2jgevpvsgtc9zwn6dただ、アニメサイトを作ることを考えると、テレビアニメも劇場版アニメも両方クエリしたいこともありそうですよね。そうなると話が複雑になってきます。
「日本のテレビアニメシリーズ(
Q63952888)」は「アニメシリーズ(Q117467261)」のサブクラス(subclass of;wdt:P279)で、それがさらに「アニメ(Q1107)」 のサブクラスになっています。ただ、この階層をいちいちリアクションに埋め込むのと大変なことになります。以下のようなクエリで「日本のテレビアニメシリーズ(Q63952888)」のすべての上位クラスが取れるのですが、54件もあります。https://query.wikidata.org/#%23%20Subclass%20hierarchy%20traversal%20for%20Q63952888%0ASELECT%20%3Fitem%20%3FitemLabel%20%3Fsuperclass%20%3FsuperclassLabel%0AWHERE%20%7B%0A%20%20%23%20Starting%20class%0A%20%20wd%3AQ63952888%20wdt%3AP279%2a%20%3Fsuperclass%20.%0A%20%20BIND%28wd%3AQ63952888%20AS%20%3Fitem%29%0A%20%20SERVICE%20wikibase%3Alabel%20%7B%20bd%3AserviceParam%20wikibase%3Alanguage%20%22%5BAUTO_LANGUAGE%5D%2Cen%22.%20%7D%0A%7D%0AORDER%20BY%20%3Fsuperclass%0A
なので、リアクション対象の
P31を埋め込む、くらいで実用上は問題ないような気がします。つまり、検索するときに 「アニメシリーズQ63952888」と「アニメ映画Q20650540」を対象にすれば、十分では、ということです。幸い、一文字タグの条件はORで効くので、複数を並べて一度にクエリできます。実際にどのくらいうまく行くかはやってみないとわからないですが。議論: どの kind を使うべきか?
一旦 kind 17 を使うことを考えてきましたが、Thingstr のイベントが Web ページに対するリアクションと混ざるのが良いことなのか、いまいち判断がついていません。
また、用途によって regular event で記録するべきか、それとも addressable event で記録すべきか、という議論もありそうです。 アニメ視聴サイトを例にあげるなら、視聴実績とか感想の変遷を記録したいならば regular event でしょうし、視聴の状態を保持したいならば addressable とするのがよさそうです。
どう思いますか?
他のアイディア
これと同じ枠組みで OpenStreetMap の Node に対してリアクションできるようにすれば Swarm のようなものも実現できるかもしれません。
用途ごとに見たいビューは違うだろうから、一貫した記録の仕方を持ちつつ、色々なサイトを作ったらいいんじゃないでしょうか。それって最高にNostrっぽくないですか?
まとめ
WikiDataやOpenStreetMapをID基盤として活用し、Nostr上でreactすることで、様々なチェックインサービス、レビューサービスを統一的なデータモデルで実現する方法について議論しました。フィードバックがあったら教えてください。むしろ実装してみてください。
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Splitpages
The simplest possible service: it splitted PDF pages in half.
Created specially to solve the problem of those scanned books that come with two pages side-by-side as if they were a single page and are much harder to read on Kindle because of that.

It required me to learn about Heroku Buildpacks though, and fork or contribute to a Heroku Buildpack that embedded a mupdf binary.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ ac8bb9b0:70278acc
2024-12-11 20:10:29
@ ac8bb9b0:70278acc
2024-12-11 20:10:29Details
- ⏲️ Prep time: 15
- 🍳 Cook time: 1 hour 30 minutes
- 🍽️ Servings: 10
Ingredients
- 1 lb. ground beef
- 1 cup celery diced
- 1 cup carrots diced
- 1 medium onion diced
- 2 medium potatoes diced
- 5 cups beef broth
- 1 15 oz. can corn, drained
- 1 8 oz. can tomato sauce
- 1 28 oz. can diced tomatoes
- 1 teaspoon salt
- 1 teaspoon Italian seasoning
- 1 bay leaf
Directions
- In a large dutch oven (I used a 6-quart), over medium heat brown the ground beef until done. Spoon off the excess fat.
- Add the remaining ingredients and stir. Bring to a boil and reduce the heat. Allow to simmer for 1 to 1 ½ hours (with the lid on, but tilted so steam can release) or until the vegetables are tender.
- Remove the bay leaf and serve.
-
 @ 42342239:1d80db24
2024-12-19 15:26:01
@ 42342239:1d80db24
2024-12-19 15:26:01Im Frühjahr kündigte EU-Kommissarin Ursula von der Leyen an, sie wolle einen „ Europäischen Demokratieschild " schaffen, um die EU vor ausländischer Einflussnahme zu schützen. Von der Leyens Demokratieschild befindet sich derzeit in der Planungsphase. Die erklärte Absicht besteht darin, eine „ spezielle Struktur zur Bekämpfung ausländischer Informationsmanipulation und -einmischung" zu schaffen. Obwohl es als Instrument zum Schutz der Demokratie angepriesen wird, vermuten einige, dass es sich in Wirklichkeit um einen verschleierten Versuch handelt, abweichende Meinungen zu unterdrücken. Der im vergangenen Jahr verabschiedete Digital Services Act (DSA) der EU ist eng mit diesem Schild verbunden. Durch den DSA riskieren große Social-Media-Plattformen wie Elon Musks X erhebliche Geldstrafen, wenn sie den Forderungen der EU-Bürokraten nach Zensur und Moderation nicht nachkommen.
Note: This text is also available in English at substack.com. Many thanks to
stroger1@iris.tofor this German translation.Im krassen Gegensatz dazu hat sich der künftige US-Präsident Donald Trump als klarer Befürworter der Meinungsfreiheit und entschiedener Gegner der Zensur hervorgetan. Er wurde bereits von YouTube gesperrt, hat jedoch erklärt, er wolle „das linke Zensurregime zerschlagen und das Recht auf freie Meinungsäußerung für alle Amerikaner zurückfordern" . Er hat auch behauptet: „Wenn wir keine freie Meinungsäußerung haben, dann haben wir einfach kein freies Land."
Sein künftiger Vizepräsident J.D. Vance hat sogar angedeutet, dass er bereit sei, US-Militärhilfe von der Achtung der Meinungsfreiheit in den europäischen NATO-Ländern abhängig zu machen. Vances Aussage erfolgte, nachdem EU-Binnenmarktkommissar Thierry Breton vor seinem geplanten Gespräch mit Trump einen umstrittenen Brief an Musk geschickt hatte. Heute erscheint dies als unkluger Schritt, nicht zuletzt, weil er als Versuch gewertet werden kann, die US-Wahl zu beeinflussen -- etwas, das paradoxerweise dem erklärten Zweck von von der Leyens Demokratieschild (d. h. ausländische Manipulationen zu bekämpfen) widerspricht.
Wenn die NATO möchte, dass wir sie weiterhin unterstützen, und die NATO möchte, dass wir weiterhin ein gutes Mitglied dieses Militärbündnisses sind, warum respektieren Sie dann nicht die amerikanischen Werte und die freie Meinungsäußerung?
- J.D. Vance
In der EU sind Verfechter der Meinungsfreiheit in der Öffentlichkeit weniger verbreitet. In Deutschland hat Vizekanzler Robert Habeck kürzlich erklärt, er sei „überhaupt nicht glücklich darüber, was dort [auf X] passiert ... seit Elon Musk das Amt übernommen hat", und wünscht sich eine strengere Regulierung der sozialen Medien. Die Wohnung eines deutschen Rentners wurde kürzlich von der Polizei durchsucht, nachdem er ein Bild von Habeck mit einem abfälligen Kommentar veröffentlicht hatte . Die deutsche Polizei verfolgt auch einen anderen Kontoinhaber, der einen Minister als „übergewichtig" bezeichnet hat. Dieser überhaupt nicht übergewichtige Minister hat kürzlich eine Zeitung verboten , die mit der laut Meinungsumfragen zweitgrößten Partei Deutschlands, der Alternative für Deutschland (AfD), verbündet ist. Eine Partei, die 113 deutsche Parlamentarier nun offiziell verbieten wollen .
Nach dem US-Wahlergebnis stellen sich viele unbeantwortete Fragen. Wird das Weiße Haus seine Aufmerksamkeit auf die restriktivere Haltung der EU richten, die als Untergrabung der freien Meinungsäußerung angesehen werden kann? Oder droht Musks X und Chinas TikTok stattdessen ein EU-Verbot? Können EU-Länder noch mit militärischer Unterstützung aus den USA rechnen? Und wenn große amerikanische Plattformen verboten werden, wohin sollten sich die EU-Bürger stattdessen wenden? Abgesehen von russischen Alternativen gibt es keine großen europäischen Plattformen. Und wenn die Frage der Meinungsfreiheit neu überdacht wird, was bedeutet das für die Zukunft von Parteien wie der deutschen AfD?
-
 @ 6e4f2866:a76f7a29
2024-12-27 16:03:31
@ 6e4f2866:a76f7a29
2024-12-27 16:03:31Have you ever felt like you’re running as fast as you can in life, only to find yourself in the same spot? Trying to achieve goals, optimise yourself only to feel unfulfilled & lacking. That’s the hamster wheel—an exhausting, repetitive cycle that holds us captive in patterns we didn’t consciously choose. These aren’t just bad habits; they’re deep-rooted default programs born from early life experiences. Let’s explore what these hamster wheels are, how they shape us, and most importantly, how we can step off them for good.
What Are Hamster Wheels? \ \ The term #hamsterwheels ( hamstr) is a metaphor for the unconscious patterns that keep us stuck. I discovered these wheels through my own introspection & seeing these patterns in my clients. Imagine a wheel turning endlessly, powered by our own efforts but leading nowhere. These programs are often formed in childhood, when trauma, disconnection, or unmet needs force us to develop defense mechanisms to survive. They worked back then, but now they just keep us spinning.
\ The Mechanics of a Hamster Wheel \ \ Every hamster wheel has two opposing forces—gain and loss, right and wrong, attention and neglect, let down & support & unable & able. We strive to stay on the “good” side: gaining approval, being right, or receiving attention. But inevitably, the wheel flips, and we find ourselves losing, being wrong, or feeling ignored. It’s a cruel cycle of frustration that feels impossible to escape. You will be positioned on the left side or right side when you look at the wheel. One is yin dominant, non doing, unable, more of a victim. One is Yang, always doing, high achiever, seen as a winner. \ \ Left side is safe in the unableness so will self sacrifice when they are to feel able to& start to achieve. So as they climb up the wheel to the right, they will lose interest or confidence in what they are doing, either sliding back exhausted in their endeavour or flipping over into victimhood. They long to be confident & win at life but deep down feel they cannot. \ \ Right sided dwellers have to be right, are constantly striving & hate (kryptonite) feeling unable. When they feel unable they will become enraged. They are compelled to gain valuableness in their own eyes and those of others. They are usually very difficult to work with as working with a therapist makes them feel unable. They will eventually put so much energy running up the right side that they will be flung backwards into usableness often times falling into deep depression (unableness) or even attracting illness. They always attract unableness & the left sided experiences to balance themselves out. The wheel always balances itself out. This is the way of the hamster wheel.

\ \ Here’s the kicker: these wheels are powered by our deepest fears and insecurities. They keep us stuck not because we’re lazy or unmotivated, but because they’ve become our default way of operating, they are our automated defence systems.
\ Common Hamster Wheels \ \ There are five key hamster wheels that we all grapple with:
- Gain/Loss: The endless chase for more—more success, more love, more recognition—followed by the crushing fear of losing it all.
- Right/Wrong: The compulsion to always be right, which leads to the paralyzing fear of being wrong.
- Attention/Neglect: Oscillating between craving attention and fearing rejection or neglect.
- Able/Unable: Striving to prove we’re capable, only to feel crushed by moments of doubt or failure.
- Support/Let Down: Giving endlessly to others for validation, but feeling betrayed or let down when it’s not reciprocated. If you watch your thoughts closely you will see these programs or songs at the root of all your thoughts.
How Hamster Wheels Impact Your Life \ \ These patterns influence every aspect of our lives: our relationships, careers, and even our self-worth. They dictate how we act, how we think, and even how we feel. For example:
- The drive to gain approval often results in feeling unworthy.
- A relentless pursuit of success can spiral into burnout and self-criticism.
- Efforts to avoid neglect might lead to overcompensating and losing yourself in the process. And the hardest part? These wheels feel like home. They’re familiar, and stepping off them can feel terrifying. They quite literally create your reality.
\ Breaking the Cycle The good news? You can break free. It’s not easy, but it’s possible. Here’s how:
- Observe Without Judgment: Start by noticing your patterns. This is real #meditation What thoughts or actions are you repeating? Don’t judge yourself—just observe. Awareness is the first step to freedom.
- Understand the Roots: These wheels didn’t come from nowhere. They’re the result of unmet needs or childhood traumas. By understanding their origins, you can begin to dismantle their power.
- Reject External Solutions: No guru, book, or quick fix can save you. True freedom comes from within. The moment you stop looking for external validation, the wheel starts to lose its grip. You must take full responsibility for everything in your life. Only you can do this proof of work.
\ Final Thoughts Hamster wheels aren’t your fault, but they are your responsibility. They’ve been running your life long enough. Isn’t it time to take back control? Imagine stepping off the wheel, feeling the ground beneath your feet for the first time. That’s where real freedom begins. So, what hamster wheel are you on? Are you ready to step off and embrace a life of clarity, peace, and purpose? The journey starts here, with a single step: observation. Everything else flows from there.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28tempreites
My first library to get stars on GitHub, was a very stupid templating library that used just HTML and HTML attributes ("DSL-free"). I was inspired by http://microjs.com/ at the time and ended up not using the library. Probably no one ever did.
-
 @ 42342239:1d80db24
2024-12-19 09:00:14
@ 42342239:1d80db24
2024-12-19 09:00:14Germany, the EU's largest economy, is once again forced to bear the label "Europe's sick man". The economic news makes for dismal reading. Industrial production has been trending downward for a long time. Energy-intensive production has decreased by as much as 20% in just a few years. Volkswagen is closing factories. Thyssenkrupp is laying off employees and more than three million pensioners are at risk of poverty according to a study.
Germany is facing a number of major challenges, including high energy costs and increased competition from China. In 2000, Germany accounted for 8% of global industrial production, but by 2030, its share is expected to have fallen to 3%. In comparison, China accounted for 2% of global industrial production in 2000, but is expected to account for nearly half (45%) of industrial production in a few years. This is according to a report from the UN's Industrial Development Organization.
Germany's electricity prices are five times higher than China's, a situation that poses a significant obstacle to maintaining a competitive position. The three main reasons are the phase-out of nuclear power, the sabotage of Nord Stream, and the ongoing energy transition, also known as Energiewende. Upon closer inspection, it is clear that industrial production has been trending downward since the transition to a greener economy began to be prioritized.
Germany's former defense minister, EU Commission President von der Leyen, called the European Green Deal Europe's "man on the moon" moment in 2019. This year, she has launched increased focus on these green goals.
However, the EU as a whole has fallen behind the US year after year. European companies have significantly higher energy costs than their American competitors, with electricity prices 2-3 times higher and natural gas prices 4-5 times higher.
The Environmental Kuznets Curve is a model that examines the relationship between economic growth and environmental impact. The idea is that increased material prosperity initially leads to more environmental degradation, but after a certain threshold is passed, there is a gradual decrease. Decreased material prosperity can thus, according to the relationship, lead to increased environmental degradation, for example due to changed consumption habits (fewer organic products in the shopping basket).
This year's election has resulted in a historic change, where all incumbent government parties in the Western world have seen their popularity decline. The pattern appears to be repeating itself in Germany next year, where Chancellor Olaf Scholz is struggling with low confidence figures ahead of the election in February, which doesn't seem surprising. Adjusted for inflation, German wages are several percent lower than a few years ago, especially in the manufacturing industry.
Germany is still a very rich country, but the current trend towards deindustrialization and falling wages can have consequences for environmental priorities in the long run. Economic difficulties can lead to environmental issues being downgraded. Perhaps the declining support for incumbent government parties is a first sign? Somewhere along the road to poverty, people will rise up in revolt.
-
 @ d9e9fb27:d5fe5e1a
2025-01-02 16:31:34
@ d9e9fb27:d5fe5e1a
2025-01-02 16:31:34Colmar is a well known city in the region of Alsace, France. Its characteristic buildings, the narrow streets and the small river flowing through are worldwide famous.

However, it is during Christmas that the city gets the most attention. Thousands of people from all over Europe decide to spend one of the Advent weekends to wander around this beautiful city and hundreds of little wooden huts.
In fact, this town becomes a small Christmas village, with decorations and lights on every building and the famous Christmas market covering every possible inch of it.



Walking around this city really makes you feel the Christmas Spirit!
Of course, it can get really cold during this time of the year. That is why Alsatians wander around drinking the Vin Chaud (literally "Hot Wine"). This beverage is prepared by mixing sugar, various spices, such as cinnamon and cloves, and red wine. They are served in a plastic glass, which can be reused multpiple time or returned for a couple of Euros. However, every year the glass is designed differently, so many people keep it with them as a collectible!
Here is 2024 version:

This is the first time I try to do a photography reportage of the places I visit. I really hope you enjoyed it!Let me know what you think, every feedback is appreciated.
I will try to create more of them during my trips, so stay tuned!
Tuma
-
 @ f0c7506b:9ead75b8
2024-12-08 09:05:13
@ f0c7506b:9ead75b8
2024-12-08 09:05:13
Yalnızca güçlü olanların hakkıdır yaşamak.
Güçlü olan ileri gider ve saflar seyrekleşir. Ama üç beş büyük, güçlü ve tanrısal kişi güneşli ve aydınlık gözleriyle o yeni, o vaat edilmiş ülkeye ulaşacaktır. Belki binlerce yıl sonra ancak. Ve güçlü, adaleli, hükmetmek için yaratılmış elleriyle hastaların, zayıfların ve sakatların ölüleri üzerinde bir krallık kuracaklardır. Bir krallık!
Benim aradığım insanların kendileri değil, sesleridir.
Duyguları körelmiş, çeşitli düşüncelere saplanmış kalabalık hiçbir zaman ilerlemenin taşıyıcısı olamaz, kendi küçüklüğünün o küflü içgüdüsüyle kalabalığın kin ve nefretle baktığı bir kişi, bir büyük kişi, iradesinin gösterdiği yolda kimsenin gözünün yaşına bakmaksızın ilahi bir güç ve bir zafer gülümsemesiyle yürüyebilir ancak.
Bizim soyumuz da sonsuz oluşum piramidinin doruk noktasını oluşturmaktan uzaktır. Bizler de mükemmelliğe ulaşmış değiliz. Bizler de henüz olgunlaşmadık.
Şairler sevgiye övgüler döşenir; doğrusu sevginin güçlü bir şey olduğu kesin. Hüneşin bir ışınıdır sevgi, aydınlatıp nurlandırır insanı der bazıları; bazıları da insanı esrikliğe sürükleyen bir zehri kendisinde barındırdığını söyler. Gerçekten de yol açtığı sonuçlar, bir hekimin ağır bir ameliyattan önce korkudan titreyen hastaya teneffüs ettirdiği güldürücü gazınkine benzer, içinde tepinip duran acıyı unutturur hastaya.
Önemli olan, hayatta hiç değilse bir kez kutsal bir ilkbaharın yaşanmasıdır; öyle bir bahar ki, insanın gönlünü ilerideki bütün günleri altın yaldızla kaplamaya yetecek kadar ışık ve parıltıyla doldursun.
Şu hayat denen şey kötü bir işçiliğin ürünü, acemilere göre bir şey. Bu kepaze yaşam uğruna insan nelere katlanmıyor ki!
Kendisine sadakatten ayrılmadığı, yalnızca kendisinin olan bir tek bu var: Yalnızlığı.
Sahildeki üstü tenteli hasır koltuklar arkasındaki yüksek, sessiz kum tepeleri içinde yürürsen, tenteler altındaki insanları göremezsin; ama birinin bir diğerine seslendiğini, bir başkasının gevezelik ettiğini, bir ötekinin güldüğünü işitir ve anlarsın hemen: bu insan şöyle şöyle biridir diyebilirsin. Onun hayatı sevdiğini, bağrında büyük bir özlem ya da acı barındırdığını, bu acının da sesini ağlamaklı kıldığını her gülüşünde hissedersin.
-
 @ 4657dfe8:47934b3e
2024-12-18 13:42:46
@ 4657dfe8:47934b3e
2024-12-18 13:42:46Alby Hub enables creation of subaccounts, decentralizing trust and creating usecases for shared, community nodes.
Simplifying Bitcoin Wallets for Friends and Family
Alby Hub empowers you to take full control of your bitcoin and manage your payments. Through a user-friendly, self-custodial wallet with a one-click lightning node setup, you can effortlessly connect to dozens of applications. The integrated App Store provides access to popular apps like Amethyst, Damus, Stacker News, Podcasting 2.0, and a wide range of other external tools—all directly linked with your Alby Hub wallet. One of the latest and most exciting additions to Alby Hub is the Friends & Family app.
With the Friends & Family app, you can create subaccounts for friends and family, all powered by your Hub. In just a few clicks, you can set up wallets for them, giving them a smooth onboarding experience and making bitcoin accessible even to those new to the ecosystem. Think of it as a custodial wallet but with a personal touch—since you’re the one managing it, there’s a direct relationship and trust.
These subaccount holders can tap into all the channels and liquidity of your Hub without needing to handle any technical setup. Plus, you can preload their wallets with a few sats, creating a welcoming and smooth experience that’s hard to find elsewhere.
And that’s not all. Beyond providing an intuitive wallet, they can get their own lightning address, configurable payment notifications, access to Alby Go (a mobile app for payments on the go), and the Alby Browser Extension for easy web payments.
Let’s have a look how to set it up.
How to provide a wallet to Friends and Family?
- Open your Hub and find the Friends & Family app in the App Store
- Enter a name e.g. your friend’s name and click “Create subaccount”
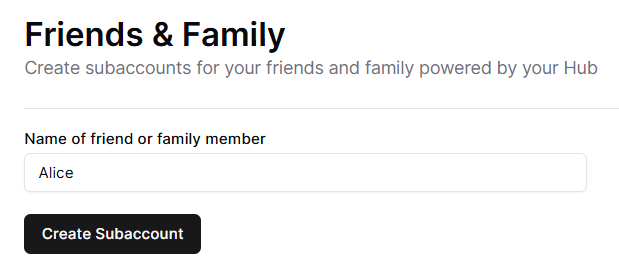
- Share the Connection Secret with your friend for the different options
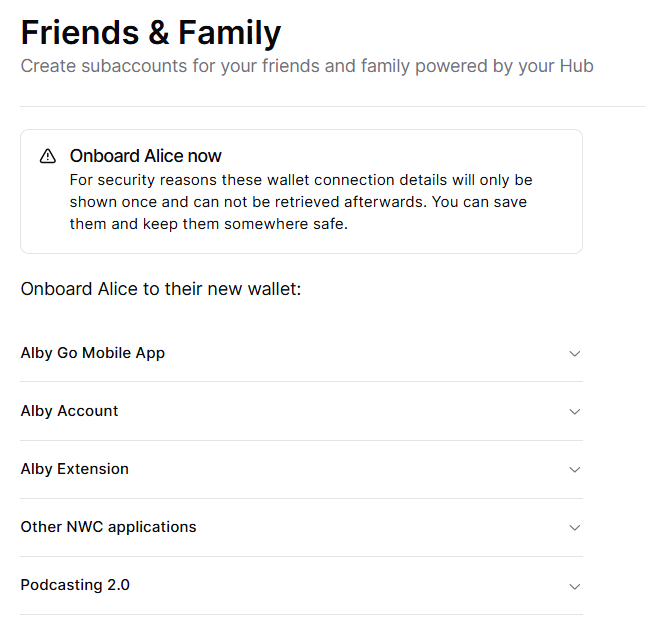
Here are two examples how your the new subaccount can be used.
Alby Go mobile App
Alby Go makes it easy to carry bitcoin in your pocket. This lightweight wallet connects directly to an Alby Hub subaccount, so your friends can pay and check transactions on the go.
Here’s how to set it up: 1. Open the Alby Go Mobile App tab in your Hub.
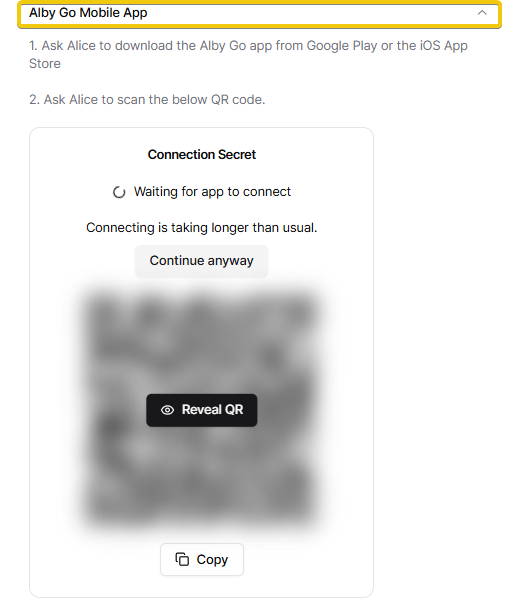 2. Copy the Connection Secret and share it with your friend if you cannot onboard them in person.
3. Your friend downloads Alby Go for Android or iOS and scans the code.
2. Copy the Connection Secret and share it with your friend if you cannot onboard them in person.
3. Your friend downloads Alby Go for Android or iOS and scans the code.And that’s it—your friend now has a bitcoin wallet in their pocket, ready for seamless transactions anytime, anywhere. 🎉
Get a Lightning Address with an Alby account
An Alby Account offers a variety of useful features that make managing bitcoin payments easy. Among these are a personalized lightning address and email payment notifications—two powerful tools that help your newly onboarded friends stay connected and informed.
To set up an Alby account for someone:
-
Open the Alby Account tab in your Hub.
-
Copy the provided URL and share it with your friend.
-
Your friend simply needs to create their Alby account and afterwards click on the provided URL.
That’s it! The wallet is instantly connected, and they’re ready to receive payments to their new lightning address. 🥳
Onboarding Family & Friends Made Easy In this article, we explored how to create subaccounts for family and friends, connect them with Alby Go, and set up an Alby account to provide a smooth onboarding experience for your loved ones—all achievable in just a few clicks.
Stay tuned as we dive into more exciting use cases for subaccounts in Alby Hub! If you have ideas for improvement,let us know.
- Open your Hub and find the Friends & Family app in the App Store
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28litepub
A Go library that abstracts all the burdensome ActivityPub things and provides just the right amount of helpers necessary to integrate an existing website into the "fediverse" (what an odious name). Made for the gravity integration.
See also
-
-
 @ a10260a2:caa23e3e
2024-10-25 01:51:45
@ a10260a2:caa23e3e
2024-10-25 01:51:45A zero-dependency, zero-framework QR code web component for Bitcoin on-chain, Lightning, and unified BIP-21 payments.
Just discovered this tool by nostr:npub18agram6s6kulwwhc638d8q8y5vysutrrvvdll2wdjxd75wp4dfjqshytrf and found it to be very useful. Also, did I mention easy-to-use?
You can find the GitHub here and a demo I made (complete with a function to check for payment) on the Bullish Prototype. 👨💻
originally posted at https://stacker.news/items/737255
-
 @ ee11a5df:b76c4e49
2024-12-24 18:49:05
@ ee11a5df:b76c4e49
2024-12-24 18:49:05China
I might be wrong, but this is how I see it
This is a post within a series I am going to call "I might be wrong, but this is how I see it"
I have repeatedly found that my understanding of China is quite different from that of many libertarian-minded Americans. And so I make this post to explain how I see it. Maybe you will learn something. Maybe I will learn something.
It seems to me that many American's see America as a shining beacon of freedom with a few small problems, and China is an evil communist country spreading communism everywhere. From my perspective, America was a shining beacon of freedom that has fallen to being typical in most ways, and which is now acting as a falling empire, and China was communist for about a decade, but turned and ran away from that as fast as they could (while not admitting it) and the result is that the US and China are not much different anymore when it comes to free markets. Except they are very different in some other respects.
China has a big problem
China has a big problem. But it is not the communism problem that most Westerners diagnose.
I argue that China is no longer communist, it is only communist in name. And that while it is not a beacon of free market principles, it is nearly as free market now as Western nations like Germany and New Zealand are (being somewhat socialist themselves).
No, China's real problem is authoritarian one-party rule. And that core problem causes all of the other problems, including its human rights abuses.
Communism and Socialism
Communism and Socialism are bad ideas. I don't want to argue it right here, but most readers will already understand this. The last thing I intend to do with this post is to bolster or defend those bad ideas. If you dear reader hold a candle for socialism, let me know and I can help you extinguish it with a future "I might be wrong, but this is how I see it" installment.
Communism is the idea of structuring a society around common ownership of the means of production, distribution, and exchange, and the idea of allocating goods and services based on need. It eliminates the concept of private property, of social classes, ultimately of money and finally of the state itself.
Back under Mao in 1958-1962 (The Great Leap Forward), China tried this (in part). Some 50+ million people died. It was an abject failure.
But due to China's real problem (authoritarianism, even worship of their leaders), the leading classes never admitted this. And even today they continue to use the word "Communist" for things that aren't communist at all, as a way to save face, and also in opposition to the United States of America and Europe.
Authorities are not eager to admit their faults. But this is not just a Chinese fault, it is a fault in human nature that affects all countries. The USA still refuses to admit they assassinated their own president JFK. They do not admit they bombed the Nord Stream pipeline.
China defines "socialism with Chinese characteristics" to mean "the leadership of the Communist Party of China". So they still keep the words socialism and communism, but they long ago dropped the meanings of those words. I'm not sure if this is a political ploy against us in the West or not.
China's Marketplace Today
Today China exhibits very few of the properties of communism.
They have some common ownership and state enterprises, but not much differently than Western countries (New Zealand owns Air New Zealand and Kiwibank and Kiwirail, etc). And there are private enterprises all over China. They compete and some succeed and some fail. You might hear about a real-estate bank collapsing. China has private property. They have mostly free markets. They have money, and the most definitely have social classes and a very strong state.
None of that is inline with what communist thinkers want. Communist thinkers in China moan that China has turned away from communism.
Deng Xiaoping who succeeded Mao and attempted to correct the massive mistake, did much when he said "to get rich is glorious."
China achieved staggering rates of economic growth. 10% annually on average since 1977. Chinese economic reform started in 1979 and has continued through successive administrations (Deng, Jiang, Hu and now Xi).
China is now the world's largest economy (by GDP in PPP terms) since 2016.
I was first made aware of China's economic growth by Jim Rogers, an American commodities expert who travelled through China (and the rest of the world from 1990-1992) and in 2007 moved to Singapore where he ensured his daughters learned to speak Mandarin, because Jim knew where the economic growth was going to happen. Jim always spoke positively of China's economic prospects, and his view was so different from the "China is a nasty communist place" view that I had grown up with that my mind opened.
How can anybody believe they are still a communist country? In what world does it make sense that communism can produce such a massively booming economy? It doesn't make sense because it is simply wrong.
What does happen is that the CPC interferes. It lets the market do what markets do, but it interferes where it thinks oversight and regulation would produce a better result.
Western nations interfere with their markets too. They have oversight and regulation. In fact some of China's planned reforms had to be put on hold by Xi due to Donald Trump's trade war with China. That's right, they were trying to be even more free market than America, but America's protectionism prodded Xi to keep control so he could fight back efficiently.
Government oversight and regulation IMHO is mostly bad because it gets out of control, and there are no market forces to correct this. This gets even more extreme in a one-party system, so I can judge that China's oversight and regulation problems are very likely worse than those in Western nations (but I have no first hand experience or evidence).
Why do you keep saying CPC?
The Communist Party of China (CPC) is the ruling party in China. That is their official name. To call them the CCP is to concede to the idea that the British and Americans get to name everybody. I'm not sure who is right, since CPC or CCP is their "English" name (in Chinese it is 中国共产党 and Westernized it is Zhōngguó Gòngchǎndǎng). Nonetheless, I'll call them CPC because that is their wish.
Social Credit System
China moved from a planned economy to a market economy in stages. They didn't want any more sudden changes (can you blame them?). In the process, many institutions that have existed in the West for a long time didn't exist in China and they had to arise somehow. IMHO market forces would have brought these about in the private sector, but the one-party CP of China instead decided to create these.
One of those institutions was a credit score system. In the West we have TransUnion and Equifax that maintain credit ratings on people, and we have S&P, Moody's and Fitch that maintain credit ratings on companies. The domain of these ratings is their financial credit-worthiness.
So the People's Bank of China developed a credit information database for it's own needs. The government picked up on the idea and started moving towards a National Credit Management System. In 2004 it became an official goal to establish a credit system compatible with a modern market system. By 2006 banks were required to report on consumer creditworthiness.
But unchecked one-party governmental power will often take a good idea (credit worthiness data shared among private parties) and systematize it and apply it top-down, creating a solution and a new problem at the same time.
Nonetheless, originally it was about credit worthiness and also criminal convictions. That is no big scary thing that some right-wing American commentators will lead you to believe. In the US for example criminal records are public, so China's Social Credit System started out being no more over-reaching in scope than what Americans have lived under their entire lives, its only fault (a severe one) being centrally planned. And that remained the case up until about 2016 (in my estimation).
But of course there is always scope creep. As it exists today, I have reason to believe that CPC officials and even A.I. use judgement calls to score someone on how moral that person has been! Of course that is not a good idea, and IMHO the problem stems from one-party rule, and authoritarian administration of ideas that should instead be handled by the private sector.
Environmental, Social, and Governance
ESG is a system that came out of a couple basic ideas. The first is that many two-party transactions actually have externalities. They don't just affect the two parties, they also affect everybody else. When you fly in an airplane, you increase the CO2 in the atmosphere that everybody has to pay for (eventually). You may dispute that example, but that is no doubt one of the motivations of ESG.
But of course the recognition of this basic issue didn't lead all people towards market solutions (well it did, but those have been mostly messed up by others), but instead led many people towards ESG, which is a social credit scoring system which applies scores based on environmental and social side-effects of market transactions.
This is not at all the same as China's social credit system, which I described above. I hope you can see the difference.
In fact, China imported ESG from the West. Chinese companies, of their free will, in an attempt to court Western capital, achieve ESG goals for those Western investors. They have been playing this ESG game for 20 years just like the entire world has, because the West has imposed this faux-morality upon them. It isn't something China exported to us, it is something we exported to them.
I think China has avoided Woke-ism
My understanding of Chinese people, based on what I've heard many Chinese people say, is that China isn't affected by the Western woke-ism epidemic. They deride Western white woke people with the term "Baizuo". They have never sent an incompetent break dancer to the Olympics because of wok-ism. Competence is highly respected as is the competition to be the most competent, which (when augmented by a one-child policy which is no longer) has produced child prodigies like no other country has.
What about predatory loans of the Belt and Road initiative?
Predatory is an odd name for loans to people in need. The World Bank makes loans to people in need. China does too. China stands in opposition to Western Empire, and in that regard they produce their own alternative BRICS institutions. This is one of them.
There is AFAIK nothing more predatory about them. It is just that in some cases the borrowers have trouble paying them back and they get foreclosed upon. I don't think this is worthy of much discussion, except that the term "predatory" seems to me to be a propaganda device.
What about foreign influence from China?
China wants to influence the world, especially its own trading partners and potential trading partners. Doing that above board is fine by me.
But some of it is undoubtedly covert. Sometimes Chinese-born people run for public office in Western countries. In New Zealand we stood down some when it became clear they were being influenced too much by the CPC while being charged with representing their local town (dual loyalty issues). If only the USA would do the same thing to their dually-loyal politicians.
And all large nations run influence operations. The USA has the CIA, for example, and claims this "soft power" is actually the better alternative to what would otherwise be military intervention (but IMHO shouldn't be either). I'm not defending such operations (I despise them), I'm just explaining how China's position of exerting influence is not only no big deal and totally expected, it pales in comparison to the United States' influence operations which often become military excursions (something China rarely ever does).
What about the Great Firewall?
Yeah, that sucks. Again, single-party authoritarian control gone to extremes.
What about Human Rights Abuses? What about the Uyghur Genocide?
I don't like them. To the extent they are occurring (and I lean towards the belief that they are occurring), I condemn them.
China has anti-terrorism and anti-extremism policies that go too far. They end up oppressing and/or criminalizing cultures that aren't Chinese enough. But especially, China punishes dissent. Disagreement with the CPC is the high crime. It is the one-party rule that causes this problem. Anybody who speaks out against the CPC or goes against the state in any way is harshly punished. This happens to Uyghurs, to Falun Gong, to Tibetans, and to any religion that is seen as subversive.
Amnesty International and the UN OHCHR have documented issues around the Xinjiang Uyghur autonomous region, Tibet, LGBT rights, death penalty, workers rights, and the Hong Kong special administrative region. I am not about to pretend I know better than they do, but to some extent they go too far.
Amnesty International says this about the USA: Discrimination and violence against LGBTI people were widespread and anti-LGBTI legislation increased. Bills were introduced to address reparations regarding slavery and its legacies. Multiple states implemented total bans on abortion or severely limited access to it. Gender-based violence disproportionately affected Indigenous women. Access to the USA for asylum seekers and migrants was still fraught with obstacles, but some nationalities continued to enjoy Temporary Protected Status. Moves were made to restrict the freedom to protest in a number of states. Black people were disproportionately affected by the use of lethal force by police. No progress was made in the abolition of the death penalty, apart from in Washington. Arbitrary and indefinite detention in the US naval base Guantánamo Bay, Cuba, continued. Despite extensive gun violence, no further firearm reform policies were considered, but President Biden did announce the creation of the White House Office of Gun Violence Prevention. The USA continued to use lethal force in countries around the world. Black people, other racialized groups and low-income people bore the brunt of the health impacts of the petrochemical industry, and the use of fossil fuels continued unabated.
Amnesty international didn't even point out that the US government quashes free speech via pressure on social media corporations (because Amnesty International is far too lefty).
So who is worse, China or the US? I'm not going to make that judgement call, but suffice it to say that in my mind, China is not obviously worse.
China violates freedom of expression, association, and assembly of all people. This is bad, and a consequence mainly of one-party rule (again, what I think is the root cause of most of their ills). They arrest, detain, potentially kill anybody who publicly disagrees openly with their government. Clearly this is an excess of authoritarianism, a cancer that is very advanced in China.
As to organ harvesting of Uyghur Muslims, I think this is a myth.
China has dealt harshly with Muslim extremism. They don't offer freedom of religion to ISIS. And Amnesty International complains about that. But practically speaking you probably shouldn't respect the extremist religion of people who want to force everybody into a global caliphate through threat of violence. As you are well aware, some extremist Muslims (<1% of Islam) believe in using violence to bring about a global caliphate. Those extremists pop up in every country and are usually dealt with harshly. China has had to deal with them too.
I have watched two different Western YouTubers travel to Xinjiang province trying to find the oppressed Uyghurs and interview them. They can't find them. What they find instead are Uyghur Muslims doing their prayers five times a day at the local mosque. And also stories that the CPC pitched in some money to help them renovate the mosque. Maybe they were afraid it was a CPC trap and so they wouldn't speak freely. Amnesty International and the UN OHCHR say more than a million are "arbitrarily detained" and I'm not going to argue otherwise. But I'd be more convinced if there were a stream of pictures and news like there is out of Gaza, and it is suspicious that there isn't.
Conclusion
China is more like a Western nation that Westerners realize. Economically, militarily, socially. It still has a very serious obstacle to overcome: one-party rule. I don't think the one-party is going to voluntarily give up power. So most probably at some point in the future there will be a revolution. But in my opinion it won't happen anytime soon. For the most part Chinese people are living high on the hog, getting rich, enjoying the good life, in positive spirits about life, and are getting along with their government quite well at present.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28questo.email
This was a thing done in a brief period I liked the idea of "indiewebcamp", a stupid movement of people saying everybody should have their site and post their lives in it.
From the GitHub postmortem:
questo.email was a service that integrated email addresses into the indieweb ecosystem by providing email-to-note and email-to-webmention triggers, which could be used for people to comment through webmention using their email addresses, and be replied, and also for people to send messages from their sites directly to the email addresses of people they knew; Questo also worked as an IndieAuth provider that used people's email addresses and Mozilla Persona.
It was live from December 2014 through December 2015.
Here's how the home page looked:

See also
- jekmentions, another thing related to "indieweb"
-
 @ fa0165a0:03397073
2024-10-23 17:19:41
@ fa0165a0:03397073
2024-10-23 17:19:41Chef's notes
This recipe is for 48 buns. Total cooking time takes at least 90 minutes, but 60 minutes of that is letting the dough rest in between processing.
The baking is a simple three-step process. 1. Making the Wheat dough 2. Making and applying the filling 3. Garnishing and baking in the oven
When done: Enjoy during Fika!
PS;
-
Can be frozen and thawed in microwave for later enjoyment as well.
-
If you need unit conversion, this site may be of help: https://www.unitconverters.net/
-
Traditionally we use something we call "Pearl sugar" which is optimal, but normal sugar or sprinkles is okay too. Pearl sugar (Pärlsocker) looks like this: https://search.brave.com/images?q=p%C3%A4rlsocker
Ingredients
- 150 g butter
- 5 dl milk
- 50 g baking yeast (normal or for sweet dough)
- 1/2 teaspoon salt
- 1-1 1/2 dl sugar
- (Optional) 2 teaspoons of crushed or grounded cardamom seeds.
- 1.4 liters of wheat flour
- Filling: 50-75 g butter, room temperature
- Filling: 1/2 - 1 dl sugar
- Filling: 1 teaspoons crushed or ground cardamom and 1 teaspoons ground cinnamon (or 2 teaspoons of cinnamon)
- Garnish: 1 egg, sugar or Almond Shavings
Directions
- Melt the butter/margarine in a saucepan.
- Pour in the milk and allow the mixture to warm reach body temperature (approx. + 37 ° C).
- Dissolve the yeast in a dough bowl with the help of the salt.
- Add the 37 ° C milk/butter mixture, sugar and if you choose to the optional cardamom. (I like this option!) and just over 2/3 of the flour.
- Work the dough shiny and smooth, about 4 minutes with a machine or 8 minutes by hand.
- Add if necessary. additional flour but save at least 1 dl for baking.
- Let the dough rise covered (by a kitchen towel), about 30 minutes.
- Work the dough into the bowl and then pick it up on a floured workbench. Knead the dough smoothly. Divide the dough into 2 parts. Roll out each piece into a rectangular cake.
- Stir together the ingredients for the filling and spread it.
- Roll up and cut each roll into 24 pieces.
- Place them in paper molds or directly on baking paper with the cut surface facing up. Let them rise covered with a baking sheet, about 30 minutes.
- Brush the buns with beaten egg and sprinkle your chosen topping.
- Bake in the middle of the oven at 250 ° C, 5-8 minutes.
- Allow to cool on a wire rack under a baking sheet.
-
-
 @ 65912a7a:5dc638bf
2024-12-08 05:33:02
@ 65912a7a:5dc638bf
2024-12-08 05:33:02Chef's notes
This is my late partner's award winning Cajun rice & beans recipe. It's an updated take on the traditional Cajun comfort food.
Chef Darin was a classically trained chef who spent 30+ years in the kitchen perfecting his recipes, and delivering authentic Cajun and Creole food to his patrons. This is a 5-star dish that will earn the respect of the most discerning Cajun afficionado. You won't be disappointed.
I suggest making this recipe exactly as directed the first time, and then make whatever adjustments you want for future batches. Also, don't cheap out on the Andouille. No Johnsonville or Hillshire Farms. Chef Aidelle's is a good choice, as is Silva's from Whole Foods. They cost a few extra bucks, but it's absolutely worth it.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 3 hours
- 🍽️ Servings: 12
Ingredients
- 16oz small red beans, dry
- 2 cups long grain white rice
- 14-16oz andouille sausage, sliced
- 8oz ham, cubed
- 1 large yellow onion, chopped
- 1 green bell pepper, chopped
- 2-3 stalks celery, chopped
- 2 tbsp garlic (12 cloves), minced
- 7 cups water
- ¼ cup olive oil
- 2 large bay leaves
- 1 tbsp parsley, dried
- 1 tsp thyme, dried
- 1 tsp Cajun seasoning
- ½ tsp cayenne pepper, dried
- ¼ tsp sage, rubbed
- 1½ tsp salt (more or less to taste)
Directions
- Soak beans in a large pot of water overnight.
- Heat oil in a large stockpot over medium heat. Cook onion, bell pepper, celery, garlic in olive oil for 3 to 4 minutes (until onion is translucent).
- Add beans, bay leaves, parsley, thyme, salt, MSG, Cajun seasoning, cayenne pepper, Sage, and water. Stir, bring to a boil, and then reduce heat to medium-low (btwn 2-3). Cover and simmer for 2½ hours.
- Remove bay leaves. Mash some of the beans. Stir Andouille and ham into beans, and simmer uncovered for an additional 30 minutes.
- Meanwhile, prepare the rice. Bring water and rice to a boil in a saucepan. Reduce heat, cover, and simmer for 20 minutes.
- Serve beans over steamed white rice.
-
 @ 5ac1f045:1a8f939a
2025-01-02 15:56:18
@ 5ac1f045:1a8f939a
2025-01-02 15:56:18GeneRo. This general AI robot represents a significant step forward in humanoid robot technology, aiming to bridge the gap between humans and robots.AMBER Robotics, a leading provider of high-end robotic actuators and bionic humanoid robot bodies, is set to revolutionize the robotics industry with the introduction of their latest innovation,
AMBER Robotics has invested significant efforts into leveraging its mature AIOS high-precision/high dynamic performance robotic actuators to create robots with diverse configurations quickly and efficiently. By utilizing standardized and serialized components, they have developed a modular approach to humanoid robot ontology, combining AI recognition and planning. This breakthrough approach enables pre-trained general-purpose humanoid robots like GeneRo to adapt and move freely, closely resembling human behavior.
GeneRo, General Robot Advancements in AI multimodal technology have enabled GeneRo and other robots to interact with humans in more intuitive and concrete ways. These robots can acquire human-like common knowledge, allowing them to perform various tasks without relying on pre-programmed instructions. GeneRo excels in unstructured environments, making it particularly valuable in everyday life and work scenarios filled with unknown obstacles.
AMBER Robotics’ technology has already gained recognition in fields such as medical rehabilitation robots, humanoid medical rehabilitation robot platforms, bionic multi-joint mechanical arms, and humanoid robot ontologies. With operations spanning major economies worldwide, the company has established itself as a global leader in high-end robotic actuators and bionic humanoid robot bodies.
Innovative Progress in General Robotics — Simple is the Best
GeneRo is the latest addition to AMBER Robotics lineup of cutting-edge robots. Standing at approximately 1.68 meters (66 feet) tall and weighing 50 kilograms (110 pounds), this humanoid robot boasts the latest generation of AI Motion Units. These units combine ultra-high torque density force-controlled joints with integrated driving and control, enabling GeneRo to move freely in a manner closely resembling human walking. The product utilizes AMBER Robotics’ self-applicable robotic joint series AIOS, high-dynamic-performance Dynamic Motion Units (DMUs) as motion actuators, and complex scene-adaptive gait balancing algorithms.
As a leading supplier in the bioinspired robot market, AMBER Robotics recognizes the need for collaboration and progress across the entire industry chain. By fostering an open and collaborative environment, AMBER Robotics aims to facilitate rapid research, exchange of ideas, and validation of breakthrough products and technologies.
GeneRo, in collaboration with AMBER Robotics, believes that humanoid robots are the ideal intelligent carriers for complex and exploratory tasks while preserving existing infrastructures. They envision the upcoming adaptive robot body, General Robot, and general artificial intelligence technology as the operating system and mobile phones of the future, propelling new technological singularities. The combined power of General Robot and general artificial intelligence will redefine human cognitive exploration and understanding of the world, addressing fundamental human needs and revolutionizing various aspects of life, including clothing, food, shelter, transportation, social activities, and business operations.
General Robot + General Artificial Intelligence Technology: Propelling New Technological Singularities
As we enter the next decade, AMBER Robotics and GeneRo are committed to driving cross-industry collaboration, accelerating the low-threshold popularization of general-purpose robot bodies and artificial intelligence. With technology poised to transform human and natural evolutionary processes at an unprecedented pace, GeneRo represents an exciting glimpse into the future.
Genero, https://www.genero.one Social, https://facebook.com/GeneRoAI Email: generohub@gmail.comGeneRo. This general AI robot represents a significant step forward in humanoid robot technology, aiming to bridge the gap between humans and robots.AMBER Robotics, a leading provider of high-end robotic actuators and bionic humanoid robot bodies, is set to revolutionize the robotics industry with the introduction of their latest innovation,
 AMBER Robotics has invested significant efforts into leveraging its mature AIOS high-precision/high dynamic performance robotic actuators to create robots with diverse configurations quickly and efficiently. By utilizing standardized and serialized components, they have developed a modular approach to humanoid robot ontology, combining AI recognition and planning. This breakthrough approach enables pre-trained general-purpose humanoid robots like GeneRo to adapt and move freely, closely resembling human behavior.
AMBER Robotics has invested significant efforts into leveraging its mature AIOS high-precision/high dynamic performance robotic actuators to create robots with diverse configurations quickly and efficiently. By utilizing standardized and serialized components, they have developed a modular approach to humanoid robot ontology, combining AI recognition and planning. This breakthrough approach enables pre-trained general-purpose humanoid robots like GeneRo to adapt and move freely, closely resembling human behavior. GeneRo, General Robot
GeneRo, General RobotAdvancements in AI multimodal technology have enabled GeneRo and other robots to interact with humans in more intuitive and concrete ways. These robots can acquire human-like common knowledge, allowing them to perform various tasks without relying on pre-programmed instructions. GeneRo excels in unstructured environments, making it particularly valuable in everyday life and work scenarios filled with unknown obstacles.
AMBER Robotics’ technology has already gained recognition in fields such as medical rehabilitation robots, humanoid medical rehabilitation robot platforms, bionic multi-joint mechanical arms, and humanoid robot ontologies. With operations spanning major economies worldwide, the company has established itself as a global leader in high-end robotic actuators and bionic humanoid robot bodies.
Innovative Progress in General Robotics — Simple is the Best
GeneRo is the latest addition to AMBER Robotics lineup of cutting-edge robots. Standing at approximately 1.68 meters (66 feet) tall and weighing 50 kilograms (110 pounds), this humanoid robot boasts the latest generation of AI Motion Units. These units combine ultra-high torque density force-controlled joints with integrated driving and control, enabling GeneRo to move freely in a manner closely resembling human walking. The product utilizes AMBER Robotics’ self-applicable robotic joint series AIOS, high-dynamic-performance Dynamic Motion Units (DMUs) as motion actuators, and complex scene-adaptive gait balancing algorithms.
As a leading supplier in the bioinspired robot market, AMBER Robotics recognizes the need for collaboration and progress across the entire industry chain. By fostering an open and collaborative environment, AMBER Robotics aims to facilitate rapid research, exchange of ideas, and validation of breakthrough products and technologies.
GeneRo, in collaboration with AMBER Robotics, believes that humanoid robots are the ideal intelligent carriers for complex and exploratory tasks while preserving existing infrastructures. They envision the upcoming adaptive robot body, General Robot, and general artificial intelligence technology as the operating system and mobile phones of the future, propelling new technological singularities. The combined power of General Robot and general artificial intelligence will redefine human cognitive exploration and understanding of the world, addressing fundamental human needs and revolutionizing various aspects of life, including clothing, food, shelter, transportation, social activities, and business operations.
General Robot + General Artificial Intelligence Technology: Propelling New Technological Singularities
As we enter the next decade, AMBER Robotics and GeneRo are committed to driving cross-industry collaboration, accelerating the low-threshold popularization of general-purpose robot bodies and artificial intelligence. With technology poised to transform human and natural evolutionary processes at an unprecedented pace, GeneRo represents an exciting glimpse into the future.
Genero, https://www.genero.one\ Social, https://facebook.com/GeneRoAI\ Email: generohub@gmail.com
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ b83e6f82:73c27758
2024-12-23 19:31:31
@ b83e6f82:73c27758
2024-12-23 19:31:31Citrine 0.6.0
- Update dependencies
- Show notifications when importing, exporting, downloading events
- Change database functions to be suspending functions
Download it with zap.store, Obtainium, f-droid or download it directly in the releases page
If you like my work consider making a donation
Verifying the release
In order to verify the release, you'll need to have
gpgorgpg2installed on your system. Once you've obtained a copy (and hopefully verified that as well), you'll first need to import the keys that have signed this release if you haven't done so already:bash gpg --keyserver hkps://keys.openpgp.org --recv-keys 44F0AAEB77F373747E3D5444885822EED3A26A6DOnce you have his PGP key you can verify the release (assuming
manifest-v0.6.0.txtandmanifest-v0.6.0.txt.sigare in the current directory) with:bash gpg --verify manifest-v0.6.0.txt.sig manifest-v0.6.0.txtYou should see the following if the verification was successful:
bash gpg: Signature made Fri 13 Sep 2024 08:06:52 AM -03 gpg: using RSA key 44F0AAEB77F373747E3D5444885822EED3A26A6D gpg: Good signature from "greenart7c3 <greenart7c3@proton.me>"That will verify the signature on the main manifest page which ensures integrity and authenticity of the binaries you've downloaded locally. Next, depending on your operating system you should then re-calculate the sha256 sum of the binary, and compare that with the following hashes:
bash cat manifest-v0.6.0.txtOne can use the
shasum -a 256 <file name here>tool in order to re-compute thesha256hash of the target binary for your operating system. The produced hash should be compared with the hashes listed above and they should match exactly. -
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28idea: Rumple
a payments network based on trust channels
This is the description of a Lightning-like network that will work only with credit or trust-based channels and exist alongside the normal Lightning Network. I imagine some people will think this is undesirable and at the same time very easy to do (such that if it doesn't exist yet it must be because no one cares), but in fact it is a very desirable thing -- which I hope I can establish below -- and at the same time a very non-trivial problem to solve, as the history of Ryan Fugger's Ripple project and posterior copies of it show.
Read these first to get the full context:
- Ryan Fugger's Ripple
- Ripple and the problem of the decentralized commit
- The Lightning Network solves the problem of the decentralized commit
- Parallel Chains
Explanation about the name
Since we're copying the fundamental Ripple idea from Ryan Fugger and since the name "Ripple" is now associated with a scam coin called XRP, and since Ryan Fugger has changed the name of his old website "Ripplepay" to "Rumplepay", we will follow his lead here. If "Ripplepay" was the name of a centralized prototype to the open peer-to-peer network "Ripple", now that the centralized version is called "Rumplepay" the peer-to-peer version must be called "Rumple".
Now the idea
Basically we copy the Lightning Network, but without HTLCs or channels being opened and closed with funds committed to them on multisig Bitcoin transactions published to the blockchain. Instead we use pure trust relationships like the original Ripple concept.
And we use the blockchain commit method, but instead of spending an absurd amount of money to use the actual Bitcoin blockchain instead we use a parallel chain.
How exactly -- a protocol proposal attempt
It could work like this:
The parallel chain, or "Rumple Chain"
- We define a parallel chain with a genesis block;
- Following blocks must contain
a. the ID of the previous block; b. a list of up to 32768 entries of arbitrary 32-byte values; c. an ID constituted by sha256(the previous block ID + the merkle root of all the entries) - To be mined, each parallel block must be included in the Bitcoin chain according as explained above.
Now that we have a structure for a simple "blockchain" that is completely useless, just blocks over blocks of meaningless values, we proceed to the next step of assigning meaning to these values.
The off-chain payments network, or "Rumple Network"
- We create a network of nodes that can talk to each other via TCP messages (all details are the same as the Lightning Network, except where mentioned otherwise);
- These nodes can create trust channels to each other. These channels are backed by nothing except the willingness of one peer to pay the other what is owed.
- When Alice creates a trust channel with Bob (
Alice trusts Bob), contrary to what happens in the Lightning Network, it's A that can immediately receive payments through that channel, and everything A receives will be an IOU from Bob to Alice. So Alice should never open a channel to Bob unless Alice trusts Bob. But also Alice can choose the amount of trust it has in Bob, she can, for example, open a very small channel with Bob, which means she will only lose a few satoshis if Bob decides to exit scam her. (in the original Ripple examples these channels were always depicted as friend relationships, and they can continue being that, but it's expected -- given the experience of the Lightning Network -- that the bulk of the channels will exist between users and wallet provider nodes that will act as hubs). - As Alice receive a payment through her channel with Bob, she becomes a creditor and Bob a debtor, i.e., the balance of the channel moves a little to her side. Now she can use these funds to make payments over that channel (or make a payment that combines funds from multiple channels using MPP).
- If at any time Alice decides to close her channel with Bob, she can send all the funds she has standing there to somewhere else (for example, another channel she has with someone else, another wallet somewhere else, a shop that is selling some good or service, or a service that will aggregate all funds from all her channels and send a transaction to the Bitcoin chain on her behalf).
- If at any time Bob leaves the network Alice is entitled by Bob's cryptographic signatures to knock on his door and demand payment, or go to a judge and ask him to force Bob to pay, or share the signatures and commitments online and hurt Bob's reputation with the rest of the network (but yes, none of these things is good enough and if Bob is a very dishonest person none of these things is likely to save Alice's funds).
The payment flow
- Suppose there exists a route
Alice->Bob->Caroland Alice wants to send a payment to Carol. - First Alice reads an invoice she received from Carol. The invoice (which can be pretty similar or maybe even the same as BOLT11) contains a payment hash
hand information about how to reach Carol's node, optionally an amount. Let's say it's 100 satoshis. - Using the routing information she gathered, Alice builds an onion and sends it to Bob, at the same time she offers to Bob a "conditional IOU". That stands for a signed commitment that Alice will owe Bob an 100 satoshis if in the next 50 blocks of the Rumple Chain there appears a block containing the preimage
psuch thatsha256(p) == h. - Bob peels the onion and discovers that he must forward that payment to Carol, so he forwards the peeled onion and offers a conditional IOU to Carol with the same
h. Bob doesn't know Carol is the final recipient of the payment, it could potentially go on and on. - When Carol gets the conditional IOU from Bob, she makes a list of all the nodes who have announced themselves as miners (which is not something I have mentioned before, but nodes that are acting as miners will must announce themselves somehow) and are online and bidding for the next Rumple block. Each of these miners will have previously published a random 32-byte value
vthey they intend to include in their next block. - Carol sends payments through routes to all (or a big number) of these miners, but this time the conditional IOU contains two conditions (values that must appear in a block for the IOU to be valid):
psuch thatsha256(p) == h(the same that featured in the invoice) andv(which must be unique and constant for each miner, something that is easily verifiable by Carol beforehand). Also, instead of these conditions being valid for the next 50 blocks they are valid only for the single next block. - Now Carol broadcasts
pto the mempool and hopes one of the miners to which she sent conditional payments sees it and, allured by the possibility of cashing in Carol's payment, includespin the next block. If that does not happen, Carol can try again in the next block.
Why bother with this at all?
-
The biggest advantage of Lightning is its openness
It has been said multiple times that if trust is involved then we don't need Lightning, we can use Coinbase, or worse, Paypal. This is very wrong. Lightning is good specially because it serves as a bridge between Coinbase, Paypal, other custodial provider and someone running their own node. All these can transact freely across the network and pay each other without worrying about who is in which provider or setup.
Rumple inherits that openness. In a Rumple Network anyone is free to open new trust channels and immediately route payments to anyone else.
Also, since Rumple payments are also based on the reveal of a preimage it can do swaps with Lightning inside a payment route from day one (by which I mean one can pay from Rumple to Lightning and vice-versa).
-
Rumple fixes Lightning's fragility
Lightning is too fragile.
It's known that Lightning is vulnerable to multiple attacks -- like the flood-and-loot attack, for example, although not an attack that's easy to execute, it's still dangerous even if failed. Given the existence of these attacks, it's important to not ever open channels with random anonymous people. Some degree of trust must exist between peers.
But one does not even have to consider attacks. The creation of HTLCs is a liability that every node has to do multiple times during its life. Every initiated, received or forwarded payment require adding one HTLC then removing it from the commitment transaction.
Another issue that makes trust needed between peers is the fact that channels can be closed unilaterally. Although this is a feature, it is also a bug when considering high-fee environments. Imagine you pay $2 in fees to open a channel, your peer may close that unilaterally in the next second and then you have to pay another $15 to close the channel. The opener pays (this is also a feature that can double as a bug by itself). Even if it's not you opening the channel, a peer can open a channel with you, make a payment, then clone the channel, and now you're left with, say, an output of 800 satoshis, which is equal to zero if network fees are high.
So you should only open channels with people you know and know aren't going to actively try to hack you and people who are not going to close channels and impose unnecessary costs on you. But even considering a fully trusted Lightning Network, even if -- to be extreme -- you only opened channels with yourself, these channels would still be fragile. If some HTLC gets stuck for any reason (peer offline or some weird small incompatibility between node softwares) and you're forced to close the channel because of that, there are the extra costs of sweeping these UTXO outputs plus the total costs of closing and reopening a channel that shouldn't have been closed in the first place. Even if HTLCs don't get stuck, a fee renegotiation event during a mempool spike may cause channels to force-close, become valueless or settle for very high closing fee.
Some of these issues are mitigated by Eltoo, others by only having channels with people you trust. Others referenced above, plus the the griefing attack and in general the ability of anyone to spam the network for free with payments that can be pending forever or a lot of payments fail repeatedly makes it very fragile.
Rumple solves most of these problems by not having to touch the blockchain at all. Fee negotiation makes no sense. Opening and closing channels is free. Flood-and-loot is a non-issue. The griefing attack can be still attempted as funds in trust channels must be reserved like on Lightning, but since there should be no theoretical limit to the number of prepared payments a channel can have, the griefing must rely on actual amounts being committed, which prevents large attacks from being performed easily.
-
Rumple fixes Lightning's unsolvable reputation issues
In the Lightning Conference 2019, Rusty Russell promised there would be pre-payments on Lightning someday, since everybody was aware of potential spam issues and pre-payments would be the way to solve that. Fast-forward to November 2020 and these pre-payments have become an apparently unsolvable problem[^thread-402]: no one knows how to implement them reliably without destroying privacy completely or introducing worse problems.
Replacing these payments with tables of reputation between peers is also an unsolved problem[^reputation-lightning], for the same reasons explained in the thread above.
-
Rumple solves the hot wallet problem
Since you don't have to use Bitcoin keys or sign transactions with a Rumple node, only your channel trust is at risk at any time.
-
Rumple ends custodianship
Since no one is storing other people's funds, a big hub or wallet provider can be used in multiple payment routes, but it cannot be immediately classified as a "custodian". At best, it will be a big debtor.
-
Rumple is fun
Opening channels with strangers is boring. Opening channels with friends and people you trust even a little makes that relationship grow stronger and the trust be reinforced. (But of course, like it happens in the Lightning Network today, if Rumple is successful the bulk of trust will be from isolated users to big reliable hubs.)
Questions or potential issues
-
So many advantages, yes, but trusted? Custodial? That's easy and stupid!
Well, an enormous part of the current Lightning Network (and also onchain Bitcoin wallets) already rests on trust, mainly trust between users and custodial wallet providers like ZEBEDEE, Alby, Wallet-of-Satoshi and others. Worse: on the current Lightning Network users not only trust, they also expose their entire transaction history to these providers[^hosted-channels].
Besides that, as detailed in point 3 of the previous section, there are many unsolvable issues on the Lightning protocol that make each sovereign node dependent on some level of trust in its peers (and the network in general dependent on trusting that no one else will spam it to death).
So, given the current state of the Lightning Network, to trust peers like Rumple requires is not a giant change -- but it is still a significant change: in Rumple you shouldn't open a large trust channel with someone just because it looks trustworthy, you must personally know that person and only put in what you're willing to lose. In known brands that have reputation to lose you can probably deposit more trust, same for long-term friends, and that's all. Still it is probably good enough, given the existence of MPP payments and the fact that the purpose of Rumple is to be a payments network for day-to-day purchases and not a way to buy real estate.
-
Why would anyone run a node in this parallel chain?
I don't know. Ideally every server running a Rumple Network node will be running a Bitcoin node and a Rumple chain node. Besides using it to confirm and publish your own Rumple Network transactions it can be set to do BMM mining automatically and maybe earn some small fees comparable to running a Lightning routing node or a JoinMarket yield generator.
Also it will probably be very lightweight, as pruning is completely free and no verification-since-the-genesis-block will take place.
-
What is the maturity of the debt that exists in the Rumple Network or its legal status?
By default it is to be understood as being payable on demand for payments occurring inside the network (as credit can be used to forward or initiate payments by the creditor using that channel). But details of settlement outside the network or what happens if one of the peers disappears cannot be enforced or specified by the network.
Perhaps some standard optional settlement methods (like a Bitcoin address) can be announced and negotiated upon channel creation inside the protocol, but nothing more than that.
[^thread-402]: Read at least the first 10 messages of the thread to see how naïve proposals like you and me could have thought about are brought up and then dismantled very carefully by the group of people most committed to getting Lightning to work properly. [^reputation-lightning]: See also the footnote at Ripple and the problem of the decentralized commit. [^hosted-channels]: Although that second part can be solved by hosted channels.
-
 @ 3bf0c63f:aefa459d
2024-12-06 20:37:26
@ 3bf0c63f:aefa459d
2024-12-06 20:37:26início
"Vocês vêem? Vêem a história? Vêem alguma coisa? Me parece que estou tentando lhes contar um sonho -- fazendo uma tentativa inútil, porque nenhum relato de sonho pode transmitir a sensação de sonho, aquela mistura de absurdo, surpresa e espanto numa excitação de revolta tentando se impôr, aquela noção de ser tomado pelo incompreensível que é da própria essência dos sonhos..."
Ele ficou em silêncio por alguns instantes.
"... Não, é impossível; é impossível transmitir a sensação viva de qualquer época determinada de nossa existência -- aquela que constitui a sua verdade, o seu significado, a sua essência sutil e contundente. É impossível. Vivemos, como sonhamos -- sozinhos..."
- Livros mencionados por Olavo de Carvalho
- Antiga homepage Olavo de Carvalho
- Bitcoin explicado de um jeito correto e inteligível
- Reclamações
-
 @ 16d11430:61640947
2024-12-23 16:47:01
@ 16d11430:61640947
2024-12-23 16:47:01At the intersection of philosophy, theology, physics, biology, and finance lies a terrifying truth: the fiat monetary system, in its current form, is not just an economic framework but a silent, relentless force actively working against humanity's survival. It isn't simply a failed financial model—it is a systemic engine of destruction, both externally and within the very core of our biological existence.
The Philosophical Void of Fiat
Philosophy has long questioned the nature of value and the meaning of human existence. From Socrates to Kant, thinkers have pondered the pursuit of truth, beauty, and virtue. But in the modern age, the fiat system has hijacked this discourse. The notion of "value" in a fiat world is no longer rooted in human potential or natural resources—it is abstracted, manipulated, and controlled by central authorities with the sole purpose of perpetuating their own power. The currency is not a reflection of society’s labor or resources; it is a representation of faith in an authority that, more often than not, breaks that faith with reckless monetary policies and hidden inflation.
The fiat system has created a kind of ontological nihilism, where the idea of true value, rooted in work, creativity, and family, is replaced with speculative gambling and short-term gains. This betrayal of human purpose at the systemic level feeds into a philosophical despair: the relentless devaluation of effort, the erosion of trust, and the abandonment of shared human values. In this nihilistic economy, purpose and meaning become increasingly difficult to find, leaving millions to question the very foundation of their existence.
Theological Implications: Fiat and the Collapse of the Sacred
Religious traditions have long linked moral integrity with the stewardship of resources and the preservation of life. Fiat currency, however, corrupts these foundational beliefs. In the theological narrative of creation, humans are given dominion over the Earth, tasked with nurturing and protecting it for future generations. But the fiat system promotes the exact opposite: it commodifies everything—land, labor, and life—treating them as mere transactions on a ledger.
This disrespect for creation is an affront to the divine. In many theologies, creation is meant to be sustained, a delicate balance that mirrors the harmony of the divine order. Fiat systems—by continuously printing money and driving inflation—treat nature and humanity as expendable resources to be exploited for short-term gains, leading to environmental degradation and societal collapse. The creation narrative, in which humans are called to be stewards, is inverted. The fiat system, through its unholy alliance with unrestrained growth and unsustainable debt, is destroying the very creation it should protect.
Furthermore, the fiat system drives idolatry of power and wealth. The central banks and corporations that control the money supply have become modern-day gods, their decrees shaping the lives of billions, while the masses are enslaved by debt and inflation. This form of worship isn't overt, but it is profound. It leads to a world where people place their faith not in God or their families, but in the abstract promises of institutions that serve their own interests.
Physics and the Infinite Growth Paradox
Physics teaches us that the universe is finite—resources, energy, and space are all limited. Yet, the fiat system operates under the delusion of infinite growth. Central banks print money without concern for natural limits, encouraging an economy that assumes unending expansion. This is not only an economic fallacy; it is a physical impossibility.
In thermodynamics, the Second Law states that entropy (disorder) increases over time in any closed system. The fiat system operates as if the Earth were an infinite resource pool, perpetually able to expand without consequence. The real world, however, does not bend to these abstract concepts of infinite growth. Resources are finite, ecosystems are fragile, and human capacity is limited. Fiat currency, by promoting unsustainable consumption and growth, accelerates the depletion of resources and the degradation of natural systems that support life itself.
Even the financial “growth” driven by fiat policies leads to unsustainable bubbles—inflated stock markets, real estate, and speculative assets that burst and leave ruin in their wake. These crashes aren’t just economic—they have profound biological consequences. The cycles of boom and bust undermine communities, erode social stability, and increase anxiety and depression, all of which affect human health at a biological level.
Biology: The Fiat System and the Destruction of Human Health
Biologically, the fiat system is a cancerous growth on human society. The constant chase for growth and the devaluation of work leads to chronic stress, which is one of the leading causes of disease in modern society. The strain of living in a system that values speculation over well-being results in a biological feedback loop: rising anxiety, poor mental health, physical diseases like cardiovascular disorders, and a shortening of lifespans.
Moreover, the focus on profit and short-term returns creates a biological disconnect between humans and the planet. The fiat system fuels industries that destroy ecosystems, increase pollution, and deplete resources at unsustainable rates. These actions are not just environmentally harmful; they directly harm human biology. The degradation of the environment—whether through toxic chemicals, pollution, or resource extraction—has profound biological effects on human health, causing respiratory diseases, cancers, and neurological disorders.
The biological cost of the fiat system is not a distant theory; it is being paid every day by millions in the form of increased health risks, diseases linked to stress, and the growing burden of mental health disorders. The constant uncertainty of an inflation-driven economy exacerbates these conditions, creating a society of individuals whose bodies and minds are under constant strain. We are witnessing a systemic biological unraveling, one in which the very act of living is increasingly fraught with pain, instability, and the looming threat of collapse.
Finance as the Final Illusion
At the core of the fiat system is a fundamental illusion—that financial growth can occur without any real connection to tangible value. The abstraction of currency, the manipulation of interest rates, and the constant creation of new money hide the underlying truth: the system is built on nothing but faith. When that faith falters, the entire system collapses.
This illusion has become so deeply embedded that it now defines the human experience. Work no longer connects to production or creation—it is reduced to a transaction on a spreadsheet, a means to acquire more fiat currency in a world where value is ephemeral and increasingly disconnected from human reality.
As we pursue ever-expanding wealth, the fundamental truths of biology—interdependence, sustainability, and balance—are ignored. The fiat system’s abstract financial models serve to disconnect us from the basic realities of life: that we are part of an interconnected world where every action has a reaction, where resources are finite, and where human health, both mental and physical, depends on the stability of our environment and our social systems.
The Ultimate Extermination
In the end, the fiat system is not just an economic issue; it is a biological, philosophical, theological, and existential threat to the very survival of humanity. It is a force that devalues human effort, encourages environmental destruction, fosters inequality, and creates pain at the core of the human biological condition. It is an economic framework that leads not to prosperity, but to extermination—not just of species, but of the very essence of human well-being.
To continue on this path is to accept the slow death of our species, one based not on natural forces, but on our own choice to worship the abstract over the real, the speculative over the tangible. The fiat system isn't just a threat; it is the ultimate self-inflicted wound, a cultural and financial cancer that, if left unchecked, will destroy humanity’s chance for survival and peace.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Boardthreads
This was a very badly done service for turning a Trello list into a helpdesk UI.
Surprisingly, it had more paying users than Websites For Trello, which I was working on simultaneously and dedicating much more time to it.
The Neo4j database I used for this was a very poor choice, it was probably the cause of all the bugs.
-
 @ 2fb77d26:c47a6ee1
2024-12-08 21:08:02
@ 2fb77d26:c47a6ee1
2024-12-08 21:08:02****Der Staat geriert sich als Bewahrer von Demokratie und Menschenrechten, als singuläres Modell zur Aufrechterhaltung gesellschaftlicher Ordnung. Dabei haben die Strukturen supranationaler »Global Governance« das Konzept Nationalstaat längst obsolet gemacht. Und auch ein Blick auf das Handeln des Machtapparats Staat lässt begründete Zweifel an dessen öffentlicher Darstellung aufkommen – denn das Kerngeschäft eines jeden Staates besteht aus Unterdrückung, Raub und Mord. **
Mein exklusiver Beitrag für die zweite GEGENDRUCK, die 224 Seiten umfasst, am 15.10.2024 veröffentlicht wurde und unter www.gegendruck.eu bestellt werden kann. Nur durch die Unterstützung von analogen Formaten dieser Art wird aus der Gegenwart eine Vergangenheit, die man in der uns drohenden Zukunft noch zu rekonstruieren vermag. * Original mit Quellen: www.regenauer.press/blog/regieren-ist-ok*
»Wenn das Volk die Regierung fürchtet, haben wir Tyrannei. Wenn die Regierung das Volk fürchtet, haben wir Freiheit« – soll Thomas Jefferson, einer der Gründerväter der USA, dereinst festgehalten haben. Wer sich also in Anbetracht des Status quo noch nicht ganz si-cher ist, mit welchem Herrschaftssystem ihn die kriegslüsterne Biosicherheitsdoktrin der Postmoderne beglückt, mag in Jeffersons Worten entsprechende Inspiration finden. Denn mit Demokratie hat die ohrenbetäubende Kakofonie von Stil-, Rechts- und Sinnbrüchen selbstverständlich nichts zu tun. Die verblassende Pluralismussimulation der zurückliegen-den Dekaden mausert sich zu dem, was mental mobile Staatstheoretiker, Historiker, Philoso-phen, Journalisten und Aktivisten seit langem erwarten – einer offen kriminellen Terrorherr-schaft. Selten war klarer als jetzt: Regieren ist organisierte Kriminalität.
Folgt man Thomas Hobbes und Friedrich Nietzsche, ist der Staat ein »Ungeheuer«. Wäh-rend Hobbes diesen Umstand durchaus goutierte, fand Nietzsche ihn abstoßend. Und zwar zurecht. Denn die repressiven Züge, die das Staatskonzept seit der frühen Neuzeit kenn-zeichnen, sind inhärenter Bestandteil der Politikproduktion. Egal, welche Ideologie ein Staat vertritt, seinen Souveränitätsanspruch kann er nur mit Gewalt durchsetzen. Nach außen mit Krieg, nach innen mit dem auf konstant interpretationsoffener werdenden Gesetzen basieren-den Gewaltmonopol. Im Rahmen seiner Halbwertszeit durchläuft jedes Herrschaftskonstrukt vergleichbare Zyklen. Ist ein Staat gegründet, eine Regierung ausgerufen, institutionalisiert sie das favorisierte politische Modell – Demokratie, Sozialismus, Konservatismus, Libera-lismus, et cetera – und vereinnahmt ihre Untertanen mit Indoktrination, Zugeständnissen und moderater Autonomie. Doch Macht korrumpiert. Und macht gierig. Vor allem in repräsenta-tiven Systemen wie der korporatisierten Sozialdemokratie, wo Einfluss einen monetären Wert darstellt.
Die Folge: Lobbyismus, Korruption, Lagerbildung, Grabenkämpfe und Obszönitäten. Einer Phase relativer Freiheit und Prosperität folgt so bald eine mehr oder weniger harsche »Ent-differenzierung« (Wolfgang Merkel, 2010) – also die Auflösung alter Strukturen, Funktio-nen und Integrationsmechanismen. Die herrschenden »Machteliten« (C. Wright Mills, 1956) grenzen sich nach zwei Seiten ab. Auf der einen von regimetreuen Bewahrern des ursprüng-lichen Konzepts, den Konservativen, auf der anderen von den Gegnern »progressiver« Re-formen. Reformen, von denen zumeist die von wachsender staatlicher Machtfülle benachtei-ligte Bevölkerung betroffen ist. Diese zahlt natürlich auch die Zeche. Rechtsprechung und Medien passen sich diesem zusehends autoritären Umfeld an, um ihre Daseinsberechtigung nicht einzubüßen. Mit dem Implementierungsgrad solcher Reformprojekte aus dem Elfen-beinturm, in der Regel begleitet von ausufernder Bürokratie, wachsen die Widerstände dage-gen. Aus Autokratie wird Totalitarismus. »Erst ist es ein Polizeistaat, dann kommen die Aufstände«. Die »Mistgabeln« (Nick Hanauer, 2014). Aus der Vogelperspektive betrachtet sind es stets die gleichen zivilisatorischen Prozesse. Seit Jahrhunderten. In allen Systemen. Offen ist nur, wie brutal der Staat vorgehen muss, um sich an der Macht zu halten – und wie lange es dauert, bis die Arroganz der wenigen dennoch an der Macht der vielen erstickt.
Denn schlussendlich fällt jedes Imperium. Das lehrt die Geschichte. Hat das System den Zenit überschritten, fällt ob der grotesken Machtexzesse und Schizophrenitäten auch den konformistischsten Etatisten auf, dass die politmediale Schmierenkomödie nichts mehr mit der Realität des eigenen Lebens zu tun hat. Gewalt greift Raum. Psychische Gewalt – und physische. Demnach hat nun zweifelsohne auch der vermeintlich liberale Rechtsstaat der von supranationalen Verordnungen diktierten Gegenwart sein finales Entwicklungsstadium er-reicht: Die Tyrannei.
»Seht uns nur an. Alles ist verdreht, alles steht Kopf. Ärzte zerstören Gesundheit, Anwälte zerstören Gerechtigkeit, Psychiater zerstören Verstand, Wissenschaftler zerstören Wahr-heit, Massenmedien zerstören Information, Religionen zerstören Spiritualität und Regierun-gen zerstören die Freiheit.« (Michael Ellner)
Neu ist das alles nicht. Nur die Darreichungsformen und Machtinstrumente von Herrschaft wandeln sich über die Jahrhunderte. Die disziplinierenden Kontrollmechanismen zur Subor-dination der Massen professionalisieren sich im Rahmen des technologischen Fortschritts. So wirkt der Panoptismus der Postmoderne vor allem deshalb monströs, weil unser Gehirn evolutionär nicht darauf eingestellt ist. Es ist der Militarisierung von Information im Dauer-feuer multimedialer Infantilisierungspropaganda in den wenigsten Fällen gewachsen. Wer versucht, dieser omnipräsenten Pervertierung von Realität mit tradierten Denk- und Hand-lungsmustern zu begegnen, geht unter.
Nicht umsonst klagt der »Widerstand« in weiten Teilen über Erschöpfungszustände, Ver-schleiß, Burnout und Depression. Genau da soll er in Augen des Staatskonzeptes sein – am Ende. Aufgerieben. Entmutigt. Ohnmächtig. Dabei wäre gerade Humor das Patentrezept, um auch düsteren Zeiten ein erfülltes Leben abzugewinnen. Ein freies Leben. Denn frei wird man nicht, frei ist man – oder eben nicht. Freiheit ist eine Geisteshaltung, kein organisatori-sches Problem.
»Unsere Gesellschaft wird von Wahnsinnigen mit wahnsinnigen Zielen geführt. (…) Und ich denke, ich werde als Wahnsinniger eingesperrt, wenn ich das zum Ausdruck bringe. Das ist das Verrückte daran.« (John Lennon)
In diesem Lichte betrachtet nimmt es also kaum Wunder, dass das primäre Ziel der regieren-den Kaste darin besteht, die Bevölkerung in Angst, Armut, Abhängigkeiten und Agonie zu halten. Selbstbestimmte, selbstbewusste Individuen hätten nämlich nicht nur die Zeit, son-dern auch die mentale Kapazität und die Mittel, das Ponzi-Schema des polit-finanziellen Komplexes intellektuell wie organisatorisch zu durchdringen. Dementsprechend ist das Staatskonzept auch nicht darauf ausgelegt, das Individuum zu fördern. Es dient der Imple-mentierung eines konformistischen Kollektivismus. Die Massen sollen sich um die Flagge scharen. Wer kritische Fragen stellt und sich der Polonaise der Gutgläubigen verweigert, gilt als Landesverräter.
Doch nicht nur die vermeintlichen Häretiker sind Opfer staatlicher Willkür und Gewaltherr-schaft. Jeder Bürger stellt per se eine potenzielle Gefahr für die Machthaber dar. Dement-sprechend agiert das »Ungeheuer« Staat. Es führt einen konstanten – mehr oder weniger vernichtenden – Krieg gegen die eigene Bevölkerung. Welche Waffen in diesem Gefecht zum Einsatz kommen, erläutert ein von Wikileaks am 13. Juni 2008 veröffentlichtes Ge-heimdokument der US-Armee vom 20. September 1994. Titel: »Foreign Internal Defense Tactics, Techniques, and Procedures for Special Forces«. Zu Deutsch: Taktiken, Techniken und Verfahren zur internen Verteidigung im Ausland für Spezialeinheiten. Julian Assange nannte es einmal »das wichtigste Dokument, das Wikileaks je veröffentlichte«. Aus gutem Grund. Denn während der Titel des 219 Seiten umfassenden Strategiepapiers darauf abstellt, dass es sich um Arbeitsanweisungen für Spezialeinheiten handelt, die im Ausland operieren, sind die beschriebenen Methoden der asymmetrischen Kriegsführung genau jene, unter de-nen – neben dem Rest der Welt – auch die amerikanische Bevölkerung leidet.
Die US-Armee beschreibt im Detail, wie die verdeckt operierenden Kräfte Regierungen ab-setzen, Oppositionsgruppen infiltrieren, die Bevölkerung manipulieren und Kriege initiieren sollen. Auf Gesetze, Moral oder Kollateralschäden wird dabei keine Rücksicht genommen. Primäres Ziel – koste es, was es wolle – ist die Durchsetzung der Pax Americana im Zielge-biet. Ein paar Zitate verdeutlichen, wie das »Ungeheuer« dabei vorgeht.
»Aufstände sind nicht einfach zufällige politische Gewalt; sie sind gezielte politische Gewalt. Sie erfordern eine Führung, die Vision, Richtung, Anleitung, Koordination und organisato-rische Kohärenz bietet. Die Anführer der Aufständischen müssen ihre Sache dem Volk be-kannt machen und die Unterstützung der Bevölkerung gewinnen. (…) Ihre Ausbildung, ihr Hintergrund, ihre Familie, ihre sozialen Verbindungen und Erfahrungen prägen ihr Den-ken und die Art und Weise, wie sie ihre Ziele erreichen. Diese Faktoren prägen auch ihre Herangehensweise an die Problemlösung.« (S. 13)
»Die Ideologie von Gruppen innerhalb der Bewegung kann auf unterschiedliche Ansichten über strategische Ziele hinweisen. Gruppen können ideologische Konflikte haben, die gelöst werden müssen, bevor ein Gegner daraus Kapital schlagen kann. Die Ideologie kann wahr-scheinliche Ziele und Taktiken nahelegen. Sie beeinflusst stark die Wahrnehmung der Um-gebung durch den Aufständischen. Diese Wahrnehmung der Umgebung wiederum prägt die organisatorischen und operativen Methoden der Bewegung.« (S. 14)
»Wenn eine Situation explosiv ist, kann fast jedes Ereignis als auslösendes Ereignis dienen. Das richtige Timing kann auch in kurzer Zeit eine Flut von Ereignissen hervorrufen, sodass es schwierig ist, ein einzelnes Ereignis als die Handlung zu bezeichnen, die den Kampf aus-gelöst hat. Daher kann es hilfreicher sein, eine Reihe von Handlungen als auslösendes Er-eignis zu betrachten. Auslösende Ereignisse können historisch sein – und die Aufständi-schen erinnern die Bevölkerung an das Ereignis. Diese Technik befreit den Aufständischen davon, auf ein geeignetes Ereignis zu warten.« (S. 18)
»Oft sind es die Armen, die im Krieg kämpfen. CSDF-Programme (CSDF: Civilian Self-Defense Force) bieten der wohlhabenden Klasse die Möglichkeit, direkt und persönlich am Kampf gegen Gesetzlosigkeit und Aufstände beteiligt zu sein. Geschäftsleute und Fachleute beteiligen sich an CSDF aus einem Gefühl der bürgerlichen Pflicht, aus Stolz und aus der Notwendigkeit, ihr Vermögen zu schützen. Ihre aktive Beteiligung verleiht dem Programm Glaubwürdigkeit, stärkt die Legitimität der Regierung und verringert Klassenkonflikte. Wohlhabendes Personal kann bei der Ausstattung seiner Einheiten mithelfen. Es darf ihnen jedoch nicht gestattet sein, den Teilnehmern ein Gehalt zu zahlen.« (S. 128)
»PSYOP-Personal oder in PSYOP ausgebildete SFOD-Mitglieder (SFOD: Special Forces Operational Detachment) erleichtern die Zusammenarbeit zwischen der lokalen Bevölke-rung und dem HN-Militär (HN: Host Nation). Wenn qualifiziertes oder fähiges HN-Personal verfügbar ist, arbeitet das US-Personal durch sie. CSDF-Elemente müssen in der Anwendung von PSYOP geschult werden, um die Bevölkerung über die Vorteile zu informie-ren, die sie durch die Zusammenarbeit mit ihnen erzielen. PSYOP-Themen müssen sich an nationale und/oder fiktive Themen halten, um eine einheitliche Politik darzustellen. Es ist entscheidend, dass PSYOP zunächst an die lokale Bevölkerung gerichtet wird, um ihre Un-terstützung der Aufständischen zu beenden und ihre Akzeptanz und Zusammenarbeit für das CSDF-Programm zu gewinnen. (…) PSYOP kann die Mission unterstützen, indem es die aufständischen Kräfte bei neutralen Gruppen diskreditiert, Zwietracht unter den Auf-ständischen selbst sät und Überläuferprogramme unterstützt. Spaltungsprogramme führen zu Zwietracht, Desorganisation, niedriger Moral, Subversion und Überläufern innerhalb der aufständischen Kräfte. Wichtig sind auch nationale Programme, um Aufständische mit Angeboten von Amnestie und Belohnungen auf die Seite der Regierung zu ziehen. Die Motive für eine Kapitulation können von persönlichen Rivalitäten und Bitterkeit bis hin zu Desillusi-onierung und Entmutigung reichen. Druck seitens der Sicherheitskräfte hat Überzeugungs-kraft. (…) Alle Agenten werden genau beobachtet und diejenigen, die nicht zuverlässig sind, werden abgelöst. Wenige, zielgerichtete, zuverlässige Agenten sind besser und wirtschaftli-cher als viele schlechte. (…) Sicherheitskräfte können Einzelpersonen aus der Bevölkerung dazu bringen, Informanten zu werden. Sicherheitskräfte nutzen verschiedene Motive (Staatsbürgersinn, Patriotismus, Angst, Strafvermeidung, Dankbarkeit, Rache oder Eifer-sucht, finanzielle Belohnungen) als überzeugende Argumente. Sie nutzen die Zusicherung des Schutzes vor Repressalien als Hauptanreiz.« (S. 139, ff)
Zusammengefasst: Die Reichen bezahlen, sorgen für Stimmung und Glaubwürdigkeit, die politische Klasse passt die Vorgehensweise an lokale Strukturen, herrschende Ideologien, Demoskopie und Kommunikationsprozesse an – und die Armen werden zum Sterben an die Front geschickt. Und das sind nur kurze Einblicke in ein über 200 Seiten starkes Handbuch zum Krieg gegen die Zivilbevölkerung, die in Augen des Hegemon offenkundig nichts ande-res als Verfügungsmasse und Kanonenfutter ist. Man möchte Julian Assange beipflichten: Dieses Dokument erklärt nicht nur, warum unsere Gesellschaften, die Wirtschaft und das moralische Koordinatensystem des Homo sapiens in Auflösung begriffen sind – die Skru-pellosigkeit der im Detail beschriebenen Methoden lässt einem das Blut in den Adern gefrie-ren. Selbst nach auszugsweiser Lektüre muss man konstatieren: Nietzsche hatte Recht. Der Staat ist ein eiskaltes Ungeheuer.
Doch was ist der Staat? War es früher das klar erkenntliche Machtvehikel von Monarchen, Imperatoren, Familiendynastien und Klerus, erweckt das Staatskonzept der jüngeren Neuzeit gerne den Eindruck, es hätte sich von dieser Despotie der wenigen gelöst, stünde für sich, auf einem Fundament des Volkswillens, der sich in Verfassungen, Gesetzen und Wahlen widerspiegelt. Weit gefehlt. Auch die »Global Governance« von heute ist nichts anderes als Despotismus. Weithin kontrolliert von den gleichen Bankenkartellen, Familien, Unterneh-men und Organisationen, die seit Generationen den Lauf der Welt bestimmen. Die Regenbo-gen emanierende Pluralismussimulation der Postmoderne verbirgt diesen Umstand nur bes-ser. Sie tyrannisiert indirekt. Köpfe werden nicht mehr abgeschlagen, sondern gewaschen. Exakt so, wie es die angloamerikanischen Vordenker dieses Systems im ausgehenden 19. Jahrhundert insinuierten. Siehe Carroll Quigley, Tragedy and Hope, 1966, Kapitel »The Fu-ture in Perspective«, Seite 1247:
»Das Argument, dass die beiden Parteien entgegengesetzte Ideale und politische Ansichten vertreten sollten, eine vielleicht rechts, die andere links, ist eine törichte Idee, die nur für doktrinäre und akademische Denker akzeptabel ist. Stattdessen sollten die beiden Parteien nahezu identisch sein, sodass das amerikanische Volk die Schurken bei jeder Wahl raus-werfen kann, ohne dass es zu tiefgreifenden oder umfassenden politischen Veränderungen kommt. Die politischen Pläne, die für Amerika lebenswichtig und notwendig sind, sind nicht länger Gegenstand großer Meinungsverschiedenheiten, sondern nur noch in Einzelheiten des Verfahrens, der Priorität oder der Methode umstritten.«
Sodass nach Scheindebatten, Empörungsmanagement und Abstimmungen nicht vom allge-meinen Kurs abgewichen werden muss. Was Quigleys elitäre Zirkel – er war bis zur Veröf-fentlichung von Tragedy and Hope einer von ihnen und unterstützte ihre Ideen – für die Rückführung der 13 US-Kolonien sowie die moderne Expansion des britischen Empire vor-sahen, ist heute zentrales Element der wertewestlichen Fassadendemokratie. Symptombe-sprechung, Lippenbekenntnisse, Emotionsamplituden, »Der Dritte Weg« – »wo soziale Ge-rechtigkeit und Markt miteinander versöhnt werden sollen« – und auch nach der x-ten Wahl bleibt alles beim Alten. Ob Berlin, Brüssel, London, New York, Beirut oder Peking: Ein Potemkin’sches Dorf. Denn wir leben längst in der Idealvorstellung von Benito Mussolini, der den perfekten Faschismus als Korporatismus bezeichnete und als symbiotische Fusion der Macht von Staat und Konzernen verstand. Als »Public Private Partnership«.
»Benito Mussolini hat der modernen Sparpolitik den Weg bereitet und die Arbeiterbewe-gung unterdrückt. Liberale Ökonomen im In- und Ausland bewunderten ihn dafür«, schrieb man bei Jacobin am 6. März 2023. So zeitigt das Staatskonzept dieser Tage die gleichen ver-heerenden Folgen wie die Herrschaftskonstrukte der Vergangenheit. Vertikale Durchlässig-keit begrenzt, das Volk manipuliert, ausgebeutet und gegängelt. Anstelle von Arbeitslagern, Schlägertrupps und Exekutionskommandos machen heute Algorithmen die Drecksarbeit. Sonst hat sich kaum etwas geändert.
Stand heute leben nach Angaben von Oxfam weltweit knapp fünf Milliarden mehr Men-schen in Armut als vor 2020. Das sind die ärmsten 60 Prozent der Menschheit. Zusammen haben sie circa 20 Milliarden US-Dollar verloren. Das Gesamtvermögen der reichsten Deut-schen wuchs im gleichen Zeitraum von 89 auf 155 Milliarden US-Dollar – ein Zuwachs von 73,85 Prozent. Die 148 größten Konzerne der Welt konnten zwischen Juni 2022 und Juni 2023 circa 1,8 Billionen Dollar an Gewinnen verzeichnen – ein Anstieg von 52,5 Prozent gegenüber dem Durchschnitt der Jahre 2018 bis 2021. Der Reingewinn stieg gegenüber die-sem Zeitraum um 20 Prozent auf 700 Milliarden Dollar. Und die fünf reichsten Menschen der Welt haben ihr Vermögen seit 2020 verdoppelt. Wer vom Nachhaltigkeitskorporatismus profitiert, dürfte damit geklärt sein.
Der Normalbürger dagegen kämpft gegen steigende Steuern, Inflation und anziehende Ener-giekosten. In einem luftabschnürenden Korsett von Verträgen, Verpflichtungen und Ver-bindlichkeiten gefangen, bleibt weder Zeit noch Geld für ein Leben in Würde. Der angepass-te Regenbogendemokrat wird geboren, indoktriniert, ausgebeutet und dann bestattet. Indivi-duelle Entfaltung ist in diesem Lebensentwurf von der Stange nicht vorgesehen. Die leitme-dialen Podiumsdiskussionen um Work-Life-Balance, Gendersprache und feministische Au-ßenpolitik klingen in den Ohren der buckelnden Arbeiterklasse – und auch für weite Teilen des schwindenden Mittelstandes – wie blanker Hohn. Das Habitat des Mediazän, das nicht selten den Eindruck erweckt, man lebe in einer fehlerhaft programmierten Simulation, zwingt seinen Bewohner immer häufiger dazu, sich existenziellen Problemen zu stellen: Unterkunft, Nahrung, Fortpflanzung. Überleben.
Noch bezahlt er Jahreslizenzen für Cloud-Software, Netflix für Filme und Streamingdienste für Musik, die er früher erwarb und dann einfach besaß. Noch geht er wählen und entschei-det brav zwischen Pest und Cholera, um vier weitere Jahre nicht die Hoffnung zu verlieren. Noch glaubt, ignoriert oder kommentiert er leidensfähig die intelligenzbeleidigenden Lügen-gebilde, die als Realität vermarktet werden.
Mithin erstaunlich. Denn nicht erst seit der Corona-Krise belegen nackte Zahlen, dass der Mensch in diesem System nicht nur beraubt und unterdrückt, sondern auch als Versuchska-ninchen für den pharmakologisch-finanziellen Komplex missbraucht wird. Nürnberger Ko-dex hin oder her. Während Robert Koch vor der Schaffung dieses vermeintlichen Bollwerks für die körperliche Unversehrtheit noch ungestraft Menschenversuche in seinen kolonialen Konzentrationslagern durchführen durfte, ist das Thema seit Ende des Zweiten Weltkrieges tabu. Gesetzlich eliminiert. Angeblich. Doch bereits in den 1940er Jahren infizierte der US-Gesundheitsdienst Gefängnisinsassen und psychisch kranke Personen mit Syphilis-Erregern. Von 1946 bis 1949 weiteten die USA das Programm auf Guatemala aus und machten sich zusätzlich über Soldaten und Prostituierte her. Das Echo der angelsächsisch geprägten Eugeniklehre hallte im fortgeführten Rassismus nach.
»Schockierende Fälle wie der Tod der 49 Kinder nach Medikamententests in einem indi-schen Krankenhaus sind in der Geschichte der Medizin nichts Neues: In den USA wurde Farbigen zu Studienzwecken von 1932 bis 1972 die Syphilis-Therapie verweigert.« (SZ, Das Verbrechen von Tuskegee, 11. Mai 2010)
Am 20. September 1950 spritzte die US-Marine vor der Küste San Franciscos Mikroben in die Troposphäre, um zu testen, welche Effekte ein Angriff mit Biowaffen auf die damals 800.000 Einwohner der Stadt haben würde. 1953 startete die CIA das MK-Ultra-Programm, in dessen Rahmen abertausenden ahnungsloser Menschen LSD verabreicht wurde. Zwei Jahre später nahm »Project Whitecoat« – Projekt Weißkittel – seine Arbeit auf. Die bestand im Verlauf der folgenden 20 Jahre darin, Menschenversuche mit Hasenpest, Typhus, Gelb-fieber und Milzbrand durchzuführen. Und Ende der 60er testeten die amerikanischen Streit-kräfte Nervengas an den eigenen Soldaten. Der SPIEGEL schrieb diesbezüglich am 10. Juli 2013:
»11. Oktober, 16:25 Uhr, 26 Stunden nach Testbeginn. Kleine blutende Anomalien am lin-ken Bein festgestellt. Subjekt behauptet, es habe seinen Rasierer fallen gelassen und sich dabei ins Bein geschnitten – doch so war es nicht. Er habe seine Sommersprossen damals für Käfer gehalten, sagt Rochelle: »Die krabbelten überall unter meiner Haut herum«. Den Betreuern habe er nichts davon erzählt, es sei ihm peinlich gewesen: »Ich habe meine Ra-sierklinge genommen und versucht, die Käfer aus meiner Haut zu schneiden.« Er war längst nicht mehr selbst dazu in der Lage, die Experimente zu stoppen. Damit war die Ein-verständniserklärung Makulatur. So wie Frank Rochelle ergeht es in Edgewood mehr als 7.800 US-Soldaten; im ganzen Land sind es rund 100.000. Systematisch haben Militär und Geheimdienste die eigenen Leute seit Ende des Ersten Weltkriegs Giften, Gasen, Drogen und Psycho-Kampfstoffen ausgesetzt, darunter LSD, Sarin, Senfgas, BZ, VX, Barbiturate, Amphetamine, Chlorpromazin und immer so weiter. Nachsorgeuntersuchungen? Fehlan-zeige. Erst nach fast sechs Jahrzehnten stoppt das US-Parlament die Menschenversuche im Jahr 1975.«
Ebenfalls bis weit in die 70er hinein injizierte man US-Gefängnisinsassen Pestizide und Herbizide. Mindestens 2.600 Menschen wurden derartigen Versuchen unterzogen. Natürlich musste auch die Atombombe am lebenden Objekt getestet werden. Sowohl Frankreich als auch Großbritannien, die ehemalige Sowjetunion oder die USA schickten Menschen auf die Testgelände. Viele von ihnen segneten danach relativ rasch das Zeitliche. Bis heute kämpfen Bewohner der entsprechenden Landstriche um Entschädigungen, weil sie ihre Krebserkran-kungen der im Umland von Testgebieten gestreuten Strahlung zuschreiben. In den 70ern machte sich der Journalist Paul Jacobs auf eigene Faust daran, die Geschichte der Betroffe-nen zu dokumentieren – um 1978 selbst an Krebs zu sterben. Selbst vor Versuchen an Kin-dern schreckte das »Ungeheuer« nie zurück, wie wiederum der SPIEGEL in Ausgabe 45 vom 2. November 1986 ausführt:
»Dwayne winkte seiner Mutter zu, sie lächelte zurück, dann schloss sich die schwere Eisen-tür hinter dem todkranken Kind. Seit drei Jahren wurde Dwayne Sexton am Strahleninstitut des Atomforschungszentrums Oak Ridge im Bundesstaat Tennessee gegen Leukämie be-handelt. Er hatte eine qualvolle Knochenmark-Transplantation sowie etliche Runden von Chemotherapie hinter sich. Alles war vergeblich geblieben. Als letztes Mittel wollten die Ärz-te nun versuchen, mit massiver Bestrahlung die Krebszellen im Knochenmark des Kindes zu zerstören. Dass diese Methode riskant und – zur damaligen Zeit, 1968 – auch wenig er-probt war, teilten die Ärzte den Eltern des Kindes mit. Was sie aber verschwiegen, war, dass sie auch im Auftrag der amerikanischen Weltraumbehörde NASA arbeiteten. Sie soll-ten herausfinden, wieviel Strahlung Astronauten im All aushalten würden, ohne krank zu werden. Für die von der NASA bestellte Untersuchung erprobten die Ärzte an ihren Patien-ten, so hieß es in einem ihrer Berichte, verschiedene »therapeutische Szenarien, die aus Strahlenmengen im All abgeleitet wurden«. Im Klartext: Nicht allein medizinische Erwä-gungen zum Wohl des Patienten setzten die Höhe der Strahlendosis fest, sondern auch die Bedürfnisse der NASA. In diesem Sinn waren die Patienten lebende Versuchskaninchen.«
Mindestens 23.000 US-Amerikaner wurden von Militäreinrichtungen und Gesundheitsbe-hörden vorsätzlich verstrahlt. Zu Forschungszwecken. »Kalter Krieg gegen US-Bevölkerung« nannte es die taz am 24. Oktober 1994.
»Zwischen 1950 und 1972 finanzierte das Pentagon außerdem fünf klinische Studien über die Aufnahmefähigkeit des menschlichen Körpers von Strahlen, um Aussagen über die psy-chologischen wie biologischen Folgen von Atomexplosionen zu erhalten. Die Versuchsper-sonen waren größtenteils in Armut lebende Schwarze. (…) Bei einem anderen Experiment mussten Soldaten auf Fässern mit radioaktivem Material herumfahren, um zu prüfen, ob ihre Autos sie vor den Strahlen schützten. In Hanford im US-Bundesstaat Washington setz-ten die Militärs absichtlich eine nukleare Wolke frei, um die Verlagerung der Wolke zu un-tersuchen. Aufgrund einer plötzlichen Änderung der Wetterlage fielen die radioaktiven Teil-chen auf einem 300 Kilometer langen und 60 Kilometer breiten Gebiet nieder (…). (jW, 29. August 1997)
Der Umgang mit der indigenen Bevölkerung wirft kein besseres Licht auf die Vereinigten Staaten. Von fünf bis sieben Millionen Ureinwohnern im Jahr 1500 waren im Jahr 1900 noch 237.000 übrig. Ob Hungersnöte, Sklavenarbeit, Massaker, Umsiedlungen oder »Boar-ding Schools« – Umerziehungsinternate: Die aus Großbritannien eingereisten Siedler verüb-ten einen Genozid an den indigenen Stämmen. Nachdem die mageren Reste der stolzen Indi-anervölker in Reservate gepfercht worden waren, suchte der Staat deren Fortpflanzung mit-tels Zwangssterilisation zu verhindern. Mehr als 60.000 Indigene wurden im 20. Jahrhundert einer solch abscheulichen Behandlung unterzogen. Darüber hinaus war das Eugenik-Programm der USA, das erst 1981 endgültig eingestellt wurde, Grundlage für die Rassen-lehre des deutschen NS-Regimes.
Ähnlich ging man in Kanada vor. Seit den 1920er Jahren wurden dort tausende indigene Frauen zwangssterilisiert – bis heute – obwohl die entsprechenden Gesetze mittlerweile ab-geschafft wurden. Die tagesschau vermeldet dazu am 10. März 2024:
»Die Worte des weißen Arztes haben sich Liz (…) ins Gedächtnis gebrannt: »Es ist besser, du stimmst der Abtreibung zu. Denn wir werden dir dieses Baby wegnehmen. So oder so«. Die damals 17-jährige Kanadierin vom indigenen Volk der Anishinabe wagt es nicht, zu widersprechen. Verängstigt sitzt sie Ende der 1970er-Jahre im Behandlungsraum der Indi-an Clinic in der Provinz Ontario, einer Klinik, in der Indigene behandelt werden, damit sie an die sogenannte Zivilisation angepasst werden. (…) Die alleinerziehende Mutter sei nicht in der Lage, für ein weiteres Kind zu sorgen. Der Arzt will ihr deshalb die Eileiter abbinden und sie dadurch sterilisieren. (…) Erst Jahre später wird ihr klar: Sie ist nicht allein. Zehn-tausende indigene Frauen sind in Kanada seit den 1920er-Jahren im Einklang mit der Eu-genik-Gesetzgebung gegen ihren Willen sterilisiert worden. Und obwohl es diese Gesetze nicht mehr gibt, geschieht es bis heute, weiß Senatorin Yvonne Boyer im Kongress in Otta-wa (…). Noch immer ist Zwangssterilisation kein Tatbestand im kanadischen Strafgesetz-buch. (…) Vergangenes Jahr wurde in den Nordwest-Territorien ein Arzt bestraft, weil er 2019 eine Inuit-Frau gegen ihren Willen unfruchtbar gemacht hat. Er verlor seine Lizenz – für fünf Monate.«
Dass sich nicht nur das angloamerikanische Empire für Eugenik begeisterte, zeigt die Ein-richtung des ersten rassenbiologischen Instituts in Schweden im Jahr 1921. Zwischen 1935 und 1976 wurden dort circa 62.000 Menschen zwangssterilisiert. Die offiziellen Begrün-dungen für die Eingriffe reichten von »Mischling« über »Alkoholismus« bis zu »dämlich« und »religiös«. Sprich: Reine Willkür unter dem Deckmantel der Wissenschaft. Legalisiert vom schwedischen Staat.
Heute begegnen uns die staatlich organisierten Eugenik-Programme unter wohlklingenden Labels wie Bioethik, reproduktive Gesundheit, biosoziale Forschung und Bevölkerungspoli-tik. Seit 1954 finden die von den Vereinten Nationen (UN) organisierten Weltbevölkerungs-konferenzen statt. Die letzte im November 2019 in Nairobi (Kenia). Was bei diesen Konfe-renzen besprochen wird, lässt sich anhand eines Artikels des GUARDIAN vom 15. April 2012 oder eines Beitrags von C-Fam (Center for Family and Human Rights) erahnen:
»Großbritannien hat 166 Millionen Pfund (268 Millionen Dollar) für ein Regierungspro-gramm in Indien gespendet, das arme Frauen und Männer zwangssterilisiert. Die britische Hilfsorganisation nannte die Notwendigkeit, dem Klimawandel durch Bevölkerungsreduzie-rung zu begegnen, als Hauptgrund für die Finanzierung des missbräuchlichen indischen Programms (…). Verpfuschte Operationen verursachten Qualen, Blutungen und Todesfäl-le. In einer von der britischen Regierung ins Visier genommenen Region verblutete die 35-jährige Frau eines armen Arbeiters, die mit Zwillingen schwanger war. Einige Frauen, die während der Schwangerschaft sterilisiert wurden, erlitten Fehlgeburten. Einige wurden mit weniger als acht Dollar und einem Sari bestochen, anderen wurde mit dem Verlust ihrer Lebensmittelkarten gedroht. Manchen wurde gesagt, die Operationen dienten der allgemei-nen Gesundheitsfürsorge, und sie erfuhren den wahren Zweck erst zu spät. Kliniken erhiel-ten Prämien für mehr als dreißig Operationen pro Tag. Nichtstaatliche Mitarbeiter wurden für jede Person bezahlt, die sie zu einer Operation überredeten. Ein Chirurg, der in einem Schulgebäude arbeitete, führte in zwei Stunden 53 Operationen durch – ohne qualifiziertes Personal, fließendes Wasser oder Mittel zum Reinigen der Geräte. Berichte der indischen Regierung aus den Jahren 2006 und 2009 warnten vor Problemen mit dem Programm. Dennoch empfahl ein Bericht des britischen Ministeriums für internationale Entwicklung aus dem Jahr 2010 die weitere Unterstützung des Programms mit der Begründung, dass eine Reduzierung der Bevölkerungszahl die Treibhausgase senken würde. (…) Sterilisation ist die häufigste Methode der Familienplanung, die in Phase II des indischen Programms für Reproduktions- und Kindergesundheit eingesetzt wird, das 2005 mit britischer Finanzie-rung begann. Trotz der Enthüllungen im ersten Jahr hat Großbritannien keine Bedingungen an seine Finanzierung geknüpft. (…) Im Juli wird Großbritannien zusammen mit der Bill & Melinda Gates Stiftung einen Familienplanungsgipfel in London ausrichten. Ziel der Veran-staltung ist es, beispielloses politisches Engagement und Ressourcen von Entwicklungslän-dern, Gebern, dem privaten Sektor, der Zivilgesellschaft und anderen Partnern zu generie-ren, um den Familienplanungsbedarf von Frauen in den ärmsten Ländern der Welt bis 2020 zu decken, erklärte das britische Ministerium für internationale Entwicklung. Melinda Gates hielt kürzlich eine Rede, in der sie behauptete, dass die Hilfe bei der Empfängnisver-hütung nichts mit Bevölkerungskontrolle oder Zwangssterilisationsprogrammen zu tun ha-be.« (C-Fam, 2. Mai 2012)
»Familienplanungsbedarf«? Dass solche Programme nichts mit »Bevölkerungskontrolle« zu tun haben, ist eine infame Lüge. Schon die von Julian Huxley verfasste Grundsatzschrift der UNESCO von 1946 spricht davon, dass Eugenik wieder salonfähig gemacht werden muss. »Das Undenkbare wenigstens wieder denkbar machen«, nannte Huxley es damals. So muss auch die ungezügelte Massenmigration als Waffe im mittlerweile allgegenwärtigen Kampf der Kulturen verstanden werden. Dabei ist allerdings nicht die Migration selbst das Problem – denn auch die Migranten sind Opfer dieser Agenda – sondern der jeweilige Auslöser für diese Zuwanderungsströme. Die verarmten, verzweifelten, traumatisierten, mit falschen Ver-sprechungen gelockten und als Spaltpilz missbrauchten Menschen für die Symptome des wertwestlichen Neokolonialismus verantwortlich zu machen, greift zu kurz.
Die chaotischen Zustände auf deutschen, britischen, schwedischen und französischen Stra-ßen sind kein Zufall, sondern gewollt. Das belegt ein Strategiepapier der Vereinten Nationen, das am 21. März 2000 publiziert wurde. Titel des Dokuments: »Replacement Migration: Is it A Solution to Declining and Ageing Populations?« Übersetzt: »Ersatzmigration: Ist sie eine Lösung für schrumpfende und alternde Bevölkerungen?«. Auf 177 Seiten erläutert die Stu-die, wie Frankreich, Großbritannien, Deutschland, Italien, Japan oder Russland zurückge-hende Geburtenraten durch massenhafte Zuwanderung kompensieren sollen. Auf den Seiten 32 und 33 liest man diesbezüglich:
»Abbildung 1 zeigt einen standardisierten Vergleich der Zuwanderungsströme pro Million Einwohner (Stand: 2000). Aus diesem Vergleich geht hervor, dass im Verhältnis zur Lan-desgröße die Zahl der Einwanderer, die im Zeitraum 2000-2050 pro Jahr benötigt wird, um den Bestand der Bevölkerung im erwerbsfähigen Alter zu erhalten (Szenario IV), mit 6.500 Einwanderern auf eine Million Einwohner in Italien am höchsten ist, gefolgt von Deutschland mit 6.000 Einwanderern pro Jahr auf eine Million Einwohner. Von den in die-sem Bericht untersuchten Ländern und Regionen benötigten die Vereinigten Staaten mit et-wa 1.300 Einwanderern auf eine Million Einwohner die geringste Zahl von Einwanderern, um einen Rückgang ihrer Bevölkerung im erwerbsfähigen Alter zu verhindern.«
»Die Zahl der Einwanderer, die notwendig ist, um ein Schrumpfen der Bevölkerung im er-werbsfähigen Alter auszugleichen, übersteigt diejenige, die einen Rückgang der Gesamtbe-völkerung ausgleichen würde, um ein Erhebliches. Ob solche höheren Einwanderungszah-len zu den Optionen gehören, die den Regierungen zur Verfügung stehen, hängt zum großen Teil von den sozialen, wirtschaftlichen und politischen Verhältnissen des jeweiligen Landes beziehungsweise der jeweiligen Region ab.«
Wer also annimmt, dass die Destabilisierungskriege und Raubzüge der NATO-Hegemonie nur dem Zwecke dienten, missliebige Regierungen auszutauschen und der Rohstoffe eines Landes habhaft zu werden, liegt offenkundig falsch. Wenn das wertewestliche Imperium irgendwo Demokratie abwirft, hat es dabei auch die strategischen Ziele globaler Bevölke-rungskontrolle im Blick. Migration als Waffe – gerichtet gegen beide involvierten Parteien. Demnach kann man sich nur wünschen, dass die Gewaltausbrüche zwischen einheimischer Bevölkerung und Migranten in den verschiedenen EU-Ländern rasch ein Ende nehmen und sich die von Verzweiflung herrührende Wut beider Parteien auf das eigentliche Problem fo-kussiert: Die herrschende Kaste und ihr gesichtsloses Imperium supranationaler Organisati-onen.
Wahrlich – die Liste an staatlich organisierten, legitimierten, orchestrierten und geduldeten Gräueltaten ließe sich beliebig lange fortführen. Je nachdem, wie weit man zurückzublicken gedenkt. Viele dieser Verbrechen sind Teil der offiziellen Geschichtsschreibung. Jeder weiß es. Dennoch führt dieses Wissen um die Skrupellosigkeit eines im Kern faschistoiden Sys-tems erstaunlicherweise bis heute nicht dazu, dass sich die Menschheit auf andere Formen des Zusammenlebens, der Verwaltung und Organisation einigt. Noch immer sehnen sich die Massen nach Führung, zentraler Steuerung und Ikonen, die ihnen ein besseres Leben ver-sprechen. Dabei belegt die Zivilisationsgeschichte mehr als eindrücklich, dass es sich um leere Versprechen handelt, dass die Hoffnung auf den edlen Ritter, die rettende Wahl oder eine bessere Zukunft reine Illusion ist. Der Machtapparat Staat dient nur einem einzigen Zweck – dem Erhalt des Machtapparats.
Es bedarf demnach auch keiner Diskussion um marginale Optimierungen des herrschenden Systems. Denn wer nur Symptome behandelt, wird die Ursache der Krankheit nicht eliminie-ren. Es bedarf der konstruktiven Debatte darüber, wie dieses System in Gänze zu ersetzen ist.
Dabei gilt es, eigene Narrative zu entwickeln. Geschichten. Vorstellungen von einer freiheit-lich organisierten Zukunft. Von einem lebenswerten morgen. Für eine Zeit nach dem »Un-geheuer«. Wir brauchen Ideen, von denen wir nachfolgende Generationen begeistern kön-nen. Und damit ist nicht die technische Verbesserung des Smartphones oder eine neue App gemeint, sondern eine Utopie. Denn gegen etwas zu sein, ist einfach. Für etwas zu sein, da-gegen nicht.
So engagieren wir uns längst nicht mehr nur für den Erhalt der Meinungsfreiheit, sondern für die Bewahrung des freien Willens. Denn was im Namen des Staates – »im Namen des Volkes« – und damit im Namen jener Menschen, die den Staat durch Wahl oder Duldung legitimieren, geschah, geschieht und geschehen wird, kann kein emotional gesundes Mitglied unserer Spezies wirklich wollen.
-
 @ a853296a:209e695f
2025-01-02 15:52:12
@ a853296a:209e695f
2025-01-02 15:52:12👋 What's up, stackers! 🤠
Excited to announce our latest project: Pull That Up Jamie. Think Perplexity but private & open source.
TLDR: ✨ Why Choose Jamie?
🛠️ Fully Open Source and Transparent! ⚡ BOLT11 Bitcoin/Lightning for Anonymous Usage! 🚄 Optimized for Speed and Convenience! 🆓 Limited Free Usage Available!
💦🔒🕵️ Your Biggest Opsec Leak - Why We Tackled Search
Search + LLMs seems like the peanut butter & jelly of the internet - a great match. But at what cost? Now that LLMs and AI are here, we know that finding needles in a vast haystack of data is much easier. That means that seemingly innocuous queries and interactions you have on the internet now carry way more weight than you think. How long before we all get owned? Privacy becomes all the more important. Each query empowers those who would exploit us. Every search chips away, revealing personal details about your state of mind. Stealing your soul little by little.
Just as bitcoin gives us the opportunity to opt out of exploitative economic systems, we wanted to take bitcoin's magic freedom dust and give you the ability to opt out of exploitative search surveillance 🔒🕵️.
⚡ How Bitcoin Lightning Yet Again Fixes This
Using the Bitcoin Connect plugin, we are able to accept BOLT11 payments. BOLT11, thanks to the lightning network's onion routing topology, affords users great sender privacy:
With just a VPN + an NWC connection, you can use Pull That Up Jamie with privacy assurances that are unparalleled. For very low cost, an average person can get Jason Bourne tier opsec.
🚧🧰🏗️Building Off the Great Work of Others
Major shout out to the ⚡ lightning devs that brought BOLT11 to the point it's at and especially to the 🐝 @getalby team for the great work on Bitcoin Connect. BC makes it easy to accept bitcoin payments with very little friction or overhead.
Additionally, we took notes on great projects like Perplexica. However we found that none of them were really geared toward the combination of speed, UX, and convenience we were looking for. Most of them are designed to be run in docker containers on your machine - great for techies but not accessible to the wider population.
We rolled our own from scratch, learning a lot from these projects. We especially took note of the superb qualities afforded by the SearXNG project🔍 🌐. What is SearXNG? Let's ask Pull That Up Jamie:
SearXNG is such a gamechanger that we plan to make a bitcoin payable, AI scannable endpoint just for accessing our instance. DM us if interested.
Armed with the ability to search the web and feed context to LLMs, we can Make The Internet Private Again. We can eliminate Google from your life.
⚡ Stackers do yourselves a favor - check out https://pullthatupjamie.ai today! 🤠
Future Work
- Open source models like 🦙 Llama
- Collaborating with @TonyGiorgio and team to use their secure compute LLM 🍁 Maple - https://stacker.news/items/764869 as part of the workflow
- Expert Mode: interrogate high signal sources of your choosing like podcasts, stacker news posts and others
- A couple more secret twists to keep you guessing :)
- Suggestions? Hit us with em.
originally posted at https://stacker.news/items/833717
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28bolt12 problems
- clients can't programatically build new offers by changing a path or query params (services like zbd.gg or lnurl-pay.me won't work)
- impossible to use in a load-balanced custodian way -- since offers would have to be pregenerated and tied to a specific lightning node.
- the existence of fiat currency fields makes it so wallets have to fetch exchange rates from somewhere on the internet (or offer a bad user experience), using HTTP which hurts user privacy.
- the vendor field is misleading, can be phished very easily, not as safe as a domain name.
- onion messages are an improvement over fake HTLC-based payments as a way of transmitting data, for sure. but we must decide if they are (i) suitable for transmitting all kinds of data over the internet, a replacement for tor; or (ii) not something that will scale well or on which we can count on for the future. if there was proper incentivization for data transmission it could end up being (i), the holy grail of p2p communication over the internet, but that is a very hard problem to solve and not guaranteed to yield the desired scalability results. since not even hints of attempting to solve that are being made, it's safer to conclude it is (ii).
bolt12 limitations
- not flexible enough. there are some interesting fields defined in the spec, but who gets to add more fields later if necessary? very unclear.
- services can't return any actionable data to the users who paid for something. it's unclear how business can be conducted without an extra communication channel.
bolt12 illusions
- recurring payments is not really solved, it is just a spec that defines intervals. the actual implementation must still be done by each wallet and service. the recurring payment cannot be enforced, the wallet must still initiate the payment. even if the wallet is evil and is willing to initiate a payment without the user knowing it still needs to have funds, channels, be online, connected etc., so it's not as if the services could rely on the payments being delivered in time.
- people seem to think it will enable pushing payments to mobile wallets, which it does not and cannot.
- there is a confusion of contexts: it looks like offers are superior to lnurl-pay, for example, because they don't require domain names. domain names, though, are common and well-established among internet services and stores, because these services have websites, so this is not really an issue. it is an issue, though, for people that want to receive payments in their homes. for these, indeed, bolt12 offers a superior solution -- but at the same time bolt12 seems to be selling itself as a tool for merchants and service providers when it includes and highlights features as recurring payments and refunds.
- the privacy gains for the receiver that are promoted as being part of bolt12 in fact come from a separate proposal, blinded paths, which should work for all normal lightning payments and indeed are a very nice solution. they are (or at least were, and should be) independent from the bolt12 proposal. a separate proposal, which can be (and already is being) used right now, also improves privacy for the receiver very much anway, it's called trampoline routing.
-
 @ 5ac1f045:1a8f939a
2025-01-02 14:58:54
@ 5ac1f045:1a8f939a
2025-01-02 14:58:54每一次重大技术的突破,普通大众往往只能作为消费者被动接受而成为最终的买单人。然而,我们相信,技术的进步不应让绝大多数人失去参与的机会。如果这样的情况持续发生,那一定是创业机制出了问题。
在过去三年中,机器人莫非连续受到上海傅利叶顾捷的挑衅、侵权和种种没有道德和法律底限的侵害,经过郑重考虑,我们将以此为契机发起打击非法技术盗抢的行动倡议,旨在让更多人有机会参与并分享机器人莫非直至整个AI和机器人技术进步的高成长和收益。
第一轮:以机器人莫非受侵害事件为始!
- 参与方式简单
每一个拥有可拍照手机和公交卡的普通人,都可以参与到机器人莫非的成长受益机会中。
- 股权捐赠与激励
机器人莫非已通过老股东捐赠和激励性股权的形式,在符合各国家或地区法律许可的前提下,让每一个普通人都有机会受益于AI和机器人这两大领域的突破性创新。只要有基于正义和热情的合法举动,就可以成为机器人莫非正式认可的“有贡献的投资人”身份而受益。
- 股东权益与维权
每一个“有贡献的投资人”,将以合法的形式成为公司的直接或间接股东,可以在因上海傅利叶顾捷的盗抢行为导致公司损失的追偿行动中获益。
我们郑重提醒,本轮打击行为不涉及任何现金投入,本轮任何以“机器人莫非”名义发起的现金筹集,均为假冒和诈骗行为。
- 维权授权
每一个获得机器人莫非官方股权的个人或法人,都可以发起针对侵害机器人莫非的维权、举报、投诉和诉讼活动。我们将提供基于当地国家或地区合法框架内的的正式授权书和股东证明书。
- 风险承诺
机器人莫非正式承诺:每一个“有贡献的投资人”都不需要承担因公司亏损带来的任何直接或间接损失。也就是说,只有收益、不承担任何债务。
我们期待您的积极参与,共同维护公司权益,实现技术创新的公平共享。
我们的目标是成为一家“全民参与、全民创新、全民受益”的基于AI机器人的创新实体,让每一个有良知的人都可以分享到因AI和机器人技术进步而带来的收益和高成长性。
我们将稍后将根据综合反馈推出具体行动细则。
机器人莫非 日期:2024年6月25日
机器人莫非简介:
机器人莫非开创了标准化、系列化的机器人专用关节,结合高性能驱动器研制和发布了系列多关节机械臂B1,L1及仿生人形机器人本体和解决方案。
赢得的客户包括全球性国际际化企业、各领域细分隐形冠军企业及众多知名院校及研究机构。
**我们保留对“合格投资人”的最终解释权,到目前为止,下面这些人将不符合资格:
1,上海傅利叶顾捷本人、家人及与其三代血亲相关的人和宠物;
2,参与盗抢机器人莫非技术秘密、有形资产有关联的人(提供证据并帮助挽回损失的除外)。每一次重大技术的突破,普通大众往往只能作为消费者被动接受而成为最终的买单人。然而,我们相信,技术的进步不应让绝大多数人失去参与的机会。如果这样的情况持续发生,那一定是创业机制出了问题。
在过去三年中,机器人莫非连续受到上海傅利叶顾捷的挑衅、侵权和种种没有道德和法律底限的侵害,经过郑重考虑,我们将以此为契机发起打击非法技术盗抢的行动倡议,旨在让更多人有机会参与并分享机器人莫非直至整个AI和机器人技术进步的高成长和收益。
第一轮:以机器人莫非受侵害事件为始!
1. 参与方式简单
每一个拥有可拍照手机和公交卡的普通人,都可以参与到机器人莫非的成长受益机会中。
2. 股权捐赠与激励
机器人莫非已通过老股东捐赠和激励性股权的形式,在符合各国家或地区法律许可的前提下,让每一个普通人都有机会受益于AI和机器人这两大领域的突破性创新。只要有基于正义和热情的合法举动,就可以成为机器人莫非正式认可的“有贡献的投资人”身份而受益。
3. 股东权益与维权
每一个“有贡献的投资人”,将以合法的形式成为公司的直接或间接股东,可以在因上海傅利叶顾捷的盗抢行为导致公司损失的追偿行动中获益。
我们郑重提醒,本轮打击行为不涉及任何现金投入,本轮任何以“机器人莫非”名义发起的现金筹集,均为假冒和诈骗行为。
4. 维权授权
每一个获得机器人莫非官方股权的个人或法人,都可以发起针对侵害机器人莫非的维权、举报、投诉和诉讼活动。我们将提供基于当地国家或地区合法框架内的的正式授权书和股东证明书。
5. 风险承诺
机器人莫非正式承诺:每一个“有贡献的投资人”都不需要承担因公司亏损带来的任何直接或间接损失。也就是说,只有收益、不承担任何债务。
我们期待您的积极参与,共同维护公司权益,实现技术创新的公平共享。
我们的目标是成为一家“全民参与、全民创新、全民受益”的基于AI机器人的创新实体,让每一个有良知的人都可以分享到因AI和机器人技术进步而带来的收益和高成长性。
我们将稍后将根据综合反馈推出具体行动细则。
机器人莫非
日期:2024年6月25日
机器人莫非简介:
机器人莫非开创了标准化、系列化的机器人专用关节,结合高性能驱动器研制和发布了系列多关节机械臂B1,L1及仿生人形机器人本体和解决方案。
赢得的客户包括全球性国际际化企业、各领域细分隐形冠军企业及众多知名院校及研究机构。
**我们保留对“合格投资人”的最终解释权,到目前为止,下面这些人将不符合资格:
1,上海傅利叶顾捷本人、家人及与其三代血亲相关的人和宠物;
2,参与盗抢机器人莫非技术秘密、有形资产有关联的人(提供证据并帮助挽回损失的除外)。
-
 @ a367f9eb:0633efea
2024-12-22 21:35:22
@ a367f9eb:0633efea
2024-12-22 21:35:22I’ll admit that I was wrong about Bitcoin. Perhaps in 2013. Definitely 2017. Probably in 2018-2019. And maybe even today.
Being wrong about Bitcoin is part of finally understanding it. It will test you, make you question everything, and in the words of BTC educator and privacy advocate Matt Odell, “Bitcoin will humble you”.
I’ve had my own stumbles on the way.
In a very public fashion in 2017, after years of using Bitcoin, trying to start a company with it, using it as my primary exchange vehicle between currencies, and generally being annoying about it at parties, I let out the bear.
In an article published in my own literary magazine Devolution Review in September 2017, I had a breaking point. The article was titled “Going Bearish on Bitcoin: Cryptocurrencies are the tulip mania of the 21st century”.
It was later republished in Huffington Post and across dozens of financial and crypto blogs at the time with another, more appropriate title: “Bitcoin Has Become About The Payday, Not Its Potential”.
As I laid out, my newfound bearishness had little to do with the technology itself or the promise of Bitcoin, and more to do with the cynical industry forming around it:
In the beginning, Bitcoin was something of a revolution to me. The digital currency represented everything from my rebellious youth.
It was a decentralized, denationalized, and digital currency operating outside the traditional banking and governmental system. It used tools of cryptography and connected buyers and sellers across national borders at minimal transaction costs.
…
The 21st-century version (of Tulip mania) has welcomed a plethora of slick consultants, hazy schemes dressed up as investor possibilities, and too much wishy-washy language for anything to really make sense to anyone who wants to use a digital currency to make purchases.
While I called out Bitcoin by name at the time, on reflection, I was really talking about the ICO craze, the wishy-washy consultants, and the altcoin ponzis.
What I was articulating — without knowing it — was the frame of NgU, or “numbers go up”. Rather than advocating for Bitcoin because of its uncensorability, proof-of-work, or immutability, the common mentality among newbies and the dollar-obsessed was that Bitcoin mattered because its price was a rocket ship.
And because Bitcoin was gaining in price, affinity tokens and projects that were imperfect forks of Bitcoin took off as well.
The price alone — rather than its qualities — were the reasons why you’d hear Uber drivers, finance bros, or your gym buddy mention Bitcoin. As someone who came to Bitcoin for philosophical reasons, that just sat wrong with me.
Maybe I had too many projects thrown in my face, or maybe I was too frustrated with the UX of Bitcoin apps and sites at the time. No matter what, I’ve since learned something.
I was at least somewhat wrong.
My own journey began in early 2011. One of my favorite radio programs, Free Talk Live, began interviewing guests and having discussions on the potential of Bitcoin. They tied it directly to a libertarian vision of the world: free markets, free people, and free banking. That was me, and I was in. Bitcoin was at about $5 back then (NgU).
I followed every article I could, talked about it with guests on my college radio show, and became a devoted redditor on r/Bitcoin. At that time, at least to my knowledge, there was no possible way to buy Bitcoin where I was living. Very weak.
I was probably wrong. And very wrong for not trying to acquire by mining or otherwise.
The next year, after moving to Florida, Bitcoin was a heavy topic with a friend of mine who shared the same vision (and still does, according to the Celsius bankruptcy documents). We talked about it with passionate leftists at Occupy Tampa in 2012, all the while trying to explain the ills of Keynesian central banking, and figuring out how to use Coinbase.
I began writing more about Bitcoin in 2013, writing a guide on “How to Avoid Bank Fees Using Bitcoin,” discussing its potential legalization in Germany, and interviewing Jeremy Hansen, one of the first political candidates in the U.S. to accept Bitcoin donations.
Even up until that point, I thought Bitcoin was an interesting protocol for sending and receiving money quickly, and converting it into fiat. The global connectedness of it, plus this cypherpunk mentality divorced from government control was both useful and attractive. I thought it was the perfect go-between.
But I was wrong.
When I gave my first public speech on Bitcoin in Vienna, Austria in December 2013, I had grown obsessed with Bitcoin’s adoption on dark net markets like Silk Road.
My theory, at the time, was the number and price were irrelevant. The tech was interesting, and a novel attempt. It was unlike anything before. But what was happening on the dark net markets, which I viewed as the true free market powered by Bitcoin, was even more interesting. I thought these markets would grow exponentially and anonymous commerce via BTC would become the norm.
While the price was irrelevant, it was all about buying and selling goods without permission or license.
Now I understand I was wrong.
Just because Bitcoin was this revolutionary technology that embraced pseudonymity did not mean that all commerce would decentralize as well. It did not mean that anonymous markets were intended to be the most powerful layer in the Bitcoin stack.
What I did not even anticipate is something articulated very well by noted Bitcoin OG Pierre Rochard: Bitcoin as a savings technology.
The ability to maintain long-term savings, practice self-discipline while stacking stats, and embrace a low-time preference was just not something on the mind of the Bitcoiners I knew at the time.
Perhaps I was reading into the hype while outwardly opposing it. Or perhaps I wasn’t humble enough to understand the true value proposition that many of us have learned years later.
In the years that followed, I bought and sold more times than I can count, and I did everything to integrate it into passion projects. I tried to set up a company using Bitcoin while at my university in Prague.
My business model depended on university students being technologically advanced enough to have a mobile wallet, own their keys, and be able to make transactions on a consistent basis. Even though I was surrounded by philosophically aligned people, those who would advance that to actually put Bitcoin into practice were sparse.
This is what led me to proclaim that “Technological Literacy is Doomed” in 2016.
And I was wrong again.
Indeed, since that time, the UX of Bitcoin-only applications, wallets, and supporting tech has vastly improved and onboarded millions more people than anyone thought possible. The entrepreneurship, coding excellence, and vision offered by Bitcoiners of all stripes have renewed a sense in me that this project is something built for us all — friends and enemies alike.
While many of us were likely distracted by flashy and pumpy altcoins over the years (me too, champs), most of us have returned to the Bitcoin stable.
Fast forward to today, there are entire ecosystems of creators, activists, and developers who are wholly reliant on the magic of Bitcoin’s protocol for their life and livelihood. The options are endless. The FUD is still present, but real proof of work stands powerfully against those forces.
In addition, there are now dozens of ways to use Bitcoin privately — still without custodians or intermediaries — that make it one of the most important assets for global humanity, especially in dictatorships.
This is all toward a positive arc of innovation, freedom, and pure independence. Did I see that coming? Absolutely not.
Of course, there are probably other shots you’ve missed on Bitcoin. Price predictions (ouch), the short-term inflation hedge, or the amount of institutional investment. While all of these may be erroneous predictions in the short term, we have to realize that Bitcoin is a long arc. It will outlive all of us on the planet, and it will continue in its present form for the next generation.
Being wrong about the evolution of Bitcoin is no fault, and is indeed part of the learning curve to finally understanding it all.
When your family or friends ask you about Bitcoin after your endless sessions explaining market dynamics, nodes, how mining works, and the genius of cryptographic signatures, try to accept that there is still so much we have to learn about this decentralized digital cash.
There are still some things you’ve gotten wrong about Bitcoin, and plenty more you’ll underestimate or get wrong in the future. That’s what makes it a beautiful journey. It’s a long road, but one that remains worth it.
-
 @ a10260a2:caa23e3e
2024-10-03 16:37:37
@ a10260a2:caa23e3e
2024-10-03 16:37:37Alby Hub is configurable with several different backends. Although setting up with Cashu is considered experimental, it’s a good option to have if you don’t want to run a Lightning node.
This post will give a quick overview of the steps to connect your Alby Hub with a Cashu mint.
Before you get started, you’re going to want to have Alby Hub installed already. There are many options for this as well — Linux, StartOS, and Umbrel to name a few. You can even have Alby host it for you in their cloud.
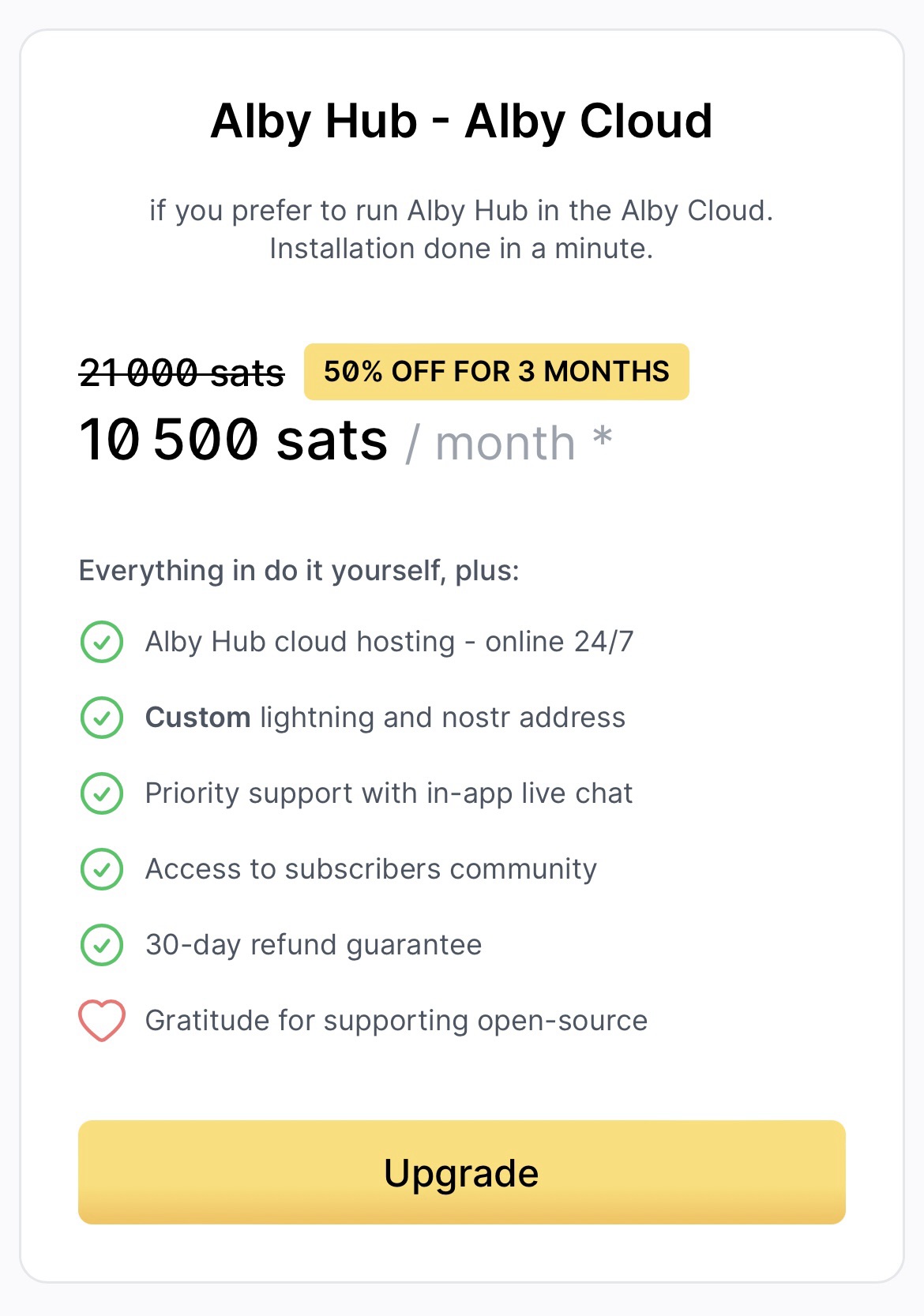
I just happen to have a Linux machine free so I went that route — the installation script made it super easy.
After the install is complete, navigating to localhost:8080 brings up this page.
- Select “Advanced Setup”
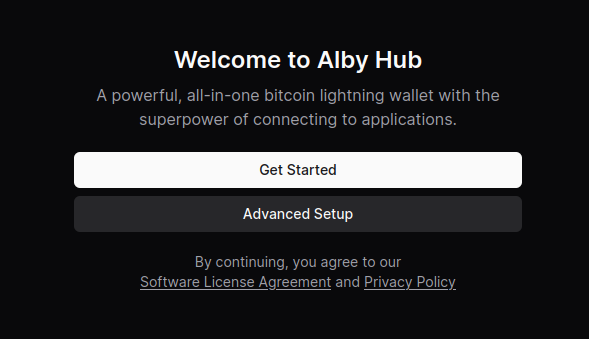
- Select “Create Wallet with Custom Node”
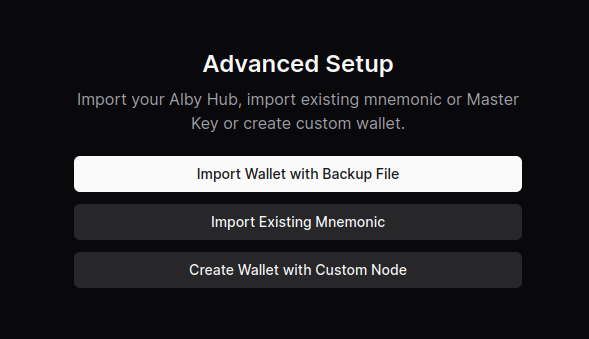
- Select “Cashu Mint”
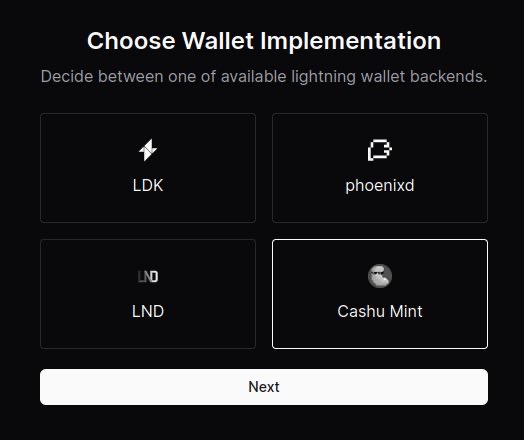
- Paste the URL of the mint you’d like to use. You can use the default one provided or click on “Find a mint” to search for others.
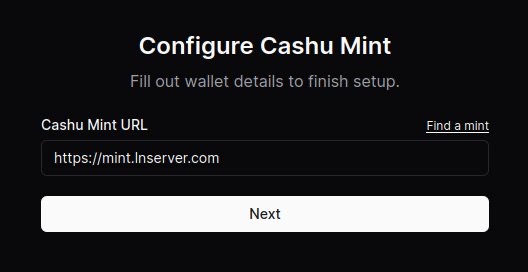
- (Optional) Connect your Alby account by requesting an authorization code. After clicking “Connect now,” a new window will open and the code displayed after signing in.
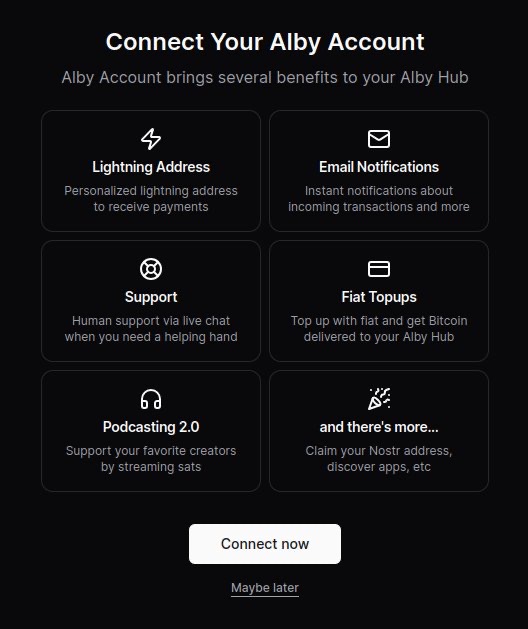
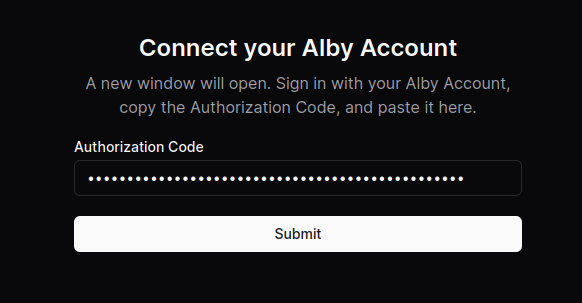
Boom. You’re all done.
Now you can use your Alby Lightning address to receive your first sats!
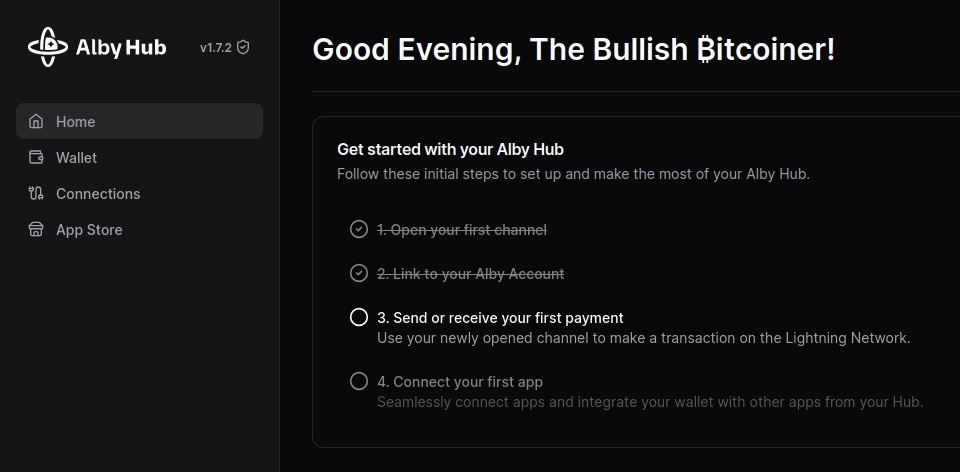
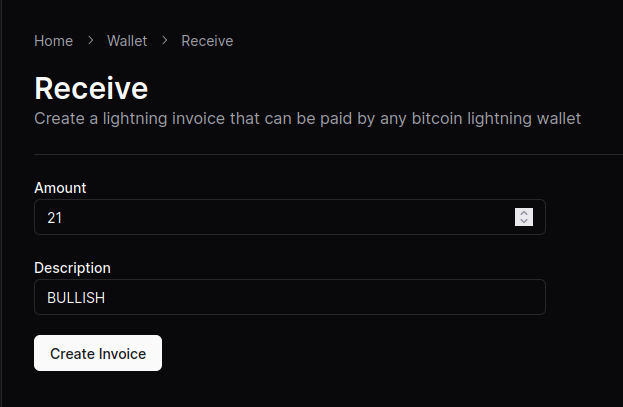
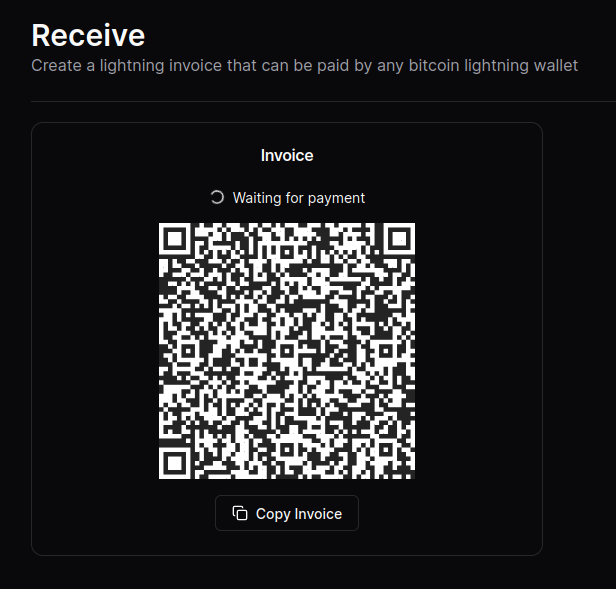
NOTE: Although the sats do make it to the wallet, the “Waiting for payment” animation seems to wait indefinitely and there’s no record in transaction history.
This seems to be a Cashu-related issue that has something to do with the preimage. An issue has been opened on GitHub if you’re curious.
Other that that, sending and receiving works like a charm.
originally posted at https://stacker.news/items/707673
-
 @ 148755e6:450c107f
2024-12-05 10:09:32
@ 148755e6:450c107f
2024-12-05 10:09:32突然荒野に行きたくなったので行ってきたエントリーです
まずは練習。高尾山へ
Nostrは古今東西ありとあらゆるオフ会が生えており、
まるで荒野に行きたいという私の意志を完全に汲み取ったかのように「紅葉を見にいこうようオフ」がそこに生えていたので参加した。(しおんさんご主催ありがとうございました)
前半1時間くらいの坂道がマジきつかったです。前半キツすぎて後半足痛かった。。 終始人がいっぱいいて渋谷かと思った。
確かに道がかなり整備されていて、逆にコンクリート故に足が疲れたのかもしれない。隣の人は途中の急な坂道で足を滑らせてて、横で転倒事故が起きるかと思いました。
山頂に行っても人がたくさんいて、迷子になりかけた。あそこはスクランブル交差点や。 そして山頂の先にあるもみじ台まで歩くと人がまばらで、まったりして蕎麦食べたりしながら休憩して下山。
登りは暑くて汗かきましたが、山頂でまったりしてると汗も引いてきて少し冷えました。
下山はスイスイ。16時近くで結構暗かったので、冬の間は早めの登頂・下山がおすすめですね。
登り2時間・下り1時間半で概ね見込み通りって感じでした。
高尾山は登ってると景色が変わります。ちょっと開けた場所に出て下の街が見えたり、草木があったり、階段があったり、参道があったり。。そういう意味では退屈しない2時間でした。
ビギナー山とはいえ、革靴やヒールのある靴で登ってる人がいてびっくり。ツルッと滑ることあると思いますので、スニーカーで登ることをお勧めします。
舐めプしてたとはいえめちゃくちゃキツかったおもひで。
更なる練習。小浅間山へ
さて私は荒野に行きたいワケなのですが、高尾山に荒野はありませんでした。更なる練習として小浅間山へ。
前日(か前々日)に雪が降ったようで、山に雪が残っておりました。
それでも都内の汚れてべちゃっとした感じの雪ではなく、粉砂糖がちょっと積もってるみたいな感じで綺麗だった。
登り前半の30分くらい、景色や道が変わらず、ずっと歩きっぱなしになってしまいました。時間みて休憩しながら行けばよかったなあ。
登るにつれて気温が下がっていくのか、積雪が厚くなっていく。
40分くらいは割と平坦な道が続きますが、突然山頂っぽいものが現れて、「これを登れっていうのかい...?」とビビるほどピーンと急な道が出てきました。(写真だと分かりづらいですね)
ただ、高尾山のコンクリート道に比べると足の疲れはそこまででした。雪道なので気をつけて歩くという意味では疲れましたが、春〜秋とかは快適に登れるんじゃないでしょうか。
山頂に到着するとドーンと浅間山が見えて圧巻。
風が強くて飛ばされる恐怖はありましたが、なんとか無事でいられました。あったかいお茶美味しかった〜。
なぜかギャルの看板があって、謎でした。写真はひとまずありません。
山頂が2箇所あって、それぞれで眺めを満喫していたら結構時間が経ってました。
小さい背丈くらいの木や足元にちょっとした植物があったり、自分的にはかなり理想の荒野に近かったです。(植物に対する解像度が低すぎる) 往復で2時間程度の山らしいんですが、なんやかんやと2時間半強くらいいた気がします。
荒野ビギナーは小浅間山に往け
というわけで、荒野に行きたい人はまずは小浅間山を登ると良いと思います。 また登りたい。
荒野部部長
一緒に高尾山・小浅間山に登ってくれた方、ありがとうございました! 個人的には来年の春までに秩父多摩甲斐国立公園に行き、来年の秋までに大山隠岐国立公園に行くという目標を立ててるんですが、 少々時間が空くので次どこに行こうかしらと考えているところです。
ヒントとしては、火山で、あまり高低差のないところだとビギナーの私にちょうど良さそうです。
とある情報筋によると伊豆大島が良さそうなので、次の機会に行けたらと思っています。
みんなで荒野に行こう!
-
 @ c4f5e7a7:8856cac7
2024-09-27 08:20:16
@ c4f5e7a7:8856cac7
2024-09-27 08:20:16Best viewed on Habla, YakiHonne or Highlighter.
TL;DR
This article explores the links between public, community-driven data sources (such as OpenStreetMap) and private, cryptographically-owned data found on networks such as Nostr.
The following concepts are explored:
- Attestations: Users signalling to their social graph that they believe something to be true by publishing Attestations. These social proofs act as a decentralised verification system that leverages your web-of-trust.
- Proof of Place: An oracle-based system where physical letters are sent to real-world locations, confirming the corresponding digital ownership via cryptographic proofs. This binds physical locations in meatspace with their digital representations in the Nostrverse.
- Check-ins: Foursquare-style check-ins that can be verified using attestations from place owners, ensuring authenticity. This approach uses web-of-trust to validate check-ins and location ownership over time.
The goal is to leverage cryptographic ownership where necessary while preserving the open, collaborative nature of public data systems.
Open Data in a public commons has a place and should not be thrown out with the Web 2.0 bathwater.
Cognitive Dissonance
Ever since discovering Nostr in August of 2022 I've been grappling with how BTC Map - a project that helps bitcoiners find places to spend sats - should most appropriately use this new protocol.
I am assuming, dear reader, that you are somewhat familiar with Nostr - a relatively new protocol for decentralised identity and communication. If you don’t know your nsec from your npub, please take some time to read these excellent posts: Nostr is Identity for the Internet and The Power of Nostr by @max and @lyn, respectively. Nostr is so much more than a short-form social media replacement.
The social features (check-ins, reviews, etc.) that Nostr unlocks for BTC Map are clear and exciting - all your silos are indeed broken - however, something fundamental has been bothering me for a while and I think it comes down to data ownership.
For those unfamiliar, BTC Map uses OpenStreetMap (OSM) as its main geographic database. OSM is centred on the concept of a commons of objectively verifiable data that is maintained by a global community of volunteer editors; a Wikipedia for maps. There is no data ownership; the data is free (as in freedom) and anyone can edit anything. It is the data equivalent of FOSS (Free and Open Source Software) - FOSD if you will, but more commonly referred to as Open Data.
In contrast, Notes and Other Stuff on Nostr (Places in this cartographic context) are explicitly owned by the controller of the private key. These notes are free to propagate, but they are owned.
How do we reconcile the decentralised nature of Nostr, where data is cryptographically owned by individuals, with the community-managed data commons of OpenStreetMap, where no one owns the data?
Self-sovereign Identity
Before I address this coexistence question, I want to talk a little about identity as it pertains to ownership. If something is to be owned, it has to be owned by someone or something - an identity.
All identities that are not self-sovereign are, by definition, leased to you by a 3rd party. You rent your Facebook identity from Meta in exchange for your data. You rent your web domain from your DNS provider in exchange for your money.
Taken to the extreme, you rent your passport from your Government in exchange for your compliance. You are you at the pleasure of others. Where Bitcoin separates money from the state; Nostr separates identity from the state.
Or, as @nvk said recently: "Don't build your house on someone else's land.".
https://i.nostr.build/xpcCSkDg3uVw0yku.png
While we’ve had the tools for self-sovereign digital identity for decades (think PGP keys or WebAuthN), we haven't had the necessary social use cases nor the corresponding social graph to elevate these identities to the mainstream. Nostr fixes this.
Nostr is PGP for the masses and will take cryptographic identities mainstream.
Full NOSTARD?
Returning to the coexistence question: the data on OpenStreetMap isn’t directly owned by anyone, even though the physical entities the data represents might be privately owned. OSM is a data commons.
We can objectively agree on the location of a tree or a fire hydrant without needing permission to observe and record it. Sure, you could place a tree ‘on Nostr’, but why should you? Just because something can be ‘on Nostr’ doesn’t mean it should be.
https://i.nostr.build/s3So2JVAqoY4E1dI.png
There might be a dystopian future where we can't agree on what a tree is nor where it's located, but I hope we never get there. It's at this point we'll need a Wikifreedia variant of OpenStreetMap.
While integrating Nostr identities into OpenStreetMap would be valuable, the current OSM infrastructure, tools, and community already provide substantial benefits in managing this data commons without needing to go NOSTR-native - there's no need to go Full NOSTARD. H/T to @princeySOV for the original meme.
https://i.nostr.build/ot9jtM5cZtDHNKWc.png
So, how do we appropriately blend cryptographically owned data with the commons?
If a location is owned in meatspace and it's useful to signal that ownership, it should also be owned in cyberspace. Our efforts should therefore focus on entities like businesses, while allowing the commons to manage public data for as long as it can successfully mitigate the tragedy of the commons.
The remainder of this article explores how we can:
- Verify ownership of a physical place in the real world;
- Link that ownership to the corresponding digital place in cyberspace.
As a side note, I don't see private key custodianship - or, even worse, permissioned use of Places signed by another identity's key - as any more viable than the rented identities of Web 2.0.
And as we all know, the Second Law of Infodynamics (no citation!) states that:
"The total amount of sensitive information leaked will always increase over time."
This especially holds true if that data is centralised.
Not your keys, not your notes. Not your keys, not your identity.
Places and Web-of-Trust
@Arkinox has been leading the charge on the Places NIP, introducing Nostr notes (kind 37515) that represent physical locations. The draft is well-crafted, with bonus points for linking back to OSM (and other location repositories) via NIP-73 - External Content IDs (championed by @oscar of @fountain).
However, as Nostr is permissionless, authenticity poses a challenge. Just because someone claims to own a physical location on the Internet doesn’t necessarily mean they have ownership or control of that location in the real world.
Ultimately, this problem can only be solved in a decentralised way by using Web-of-Trust - using your social graph and the perspectives of trusted peers to inform your own perspective. In the context of Places, this requires your network to form a view on which digital identity (public key / npub) is truly the owner of a physical place like your local coffee shop.
This requires users to:
- Verify the owner of a Place in cyberspace is the owner of a place in meatspace.
- Signal this verification to their social graph.
Let's look at the latter idea first with the concept of Attestations ...
Attestations
A way to signal to your social graph that you believe something to be true (or false for that matter) would be by publishing an Attestation note. An Attestation note would signify to your social graph that you think something is either true or false.
Imagine you're a regular at a local coffee shop. You publish an Attestation that says the shop is real and the owner behind the Nostr public key is who they claim to be. Your friends trust you, so they start trusting the shop's digital identity too.
However, attestations applied to Places are just a single use case. The attestation concept could be more widely applied across Nostr in a variety of ways (key rotation, identity linking, etc).
Here is a recent example from @lyn that would carry more signal if it were an Attestation:
https://i.nostr.build/lZAXOEwvRIghgFY4.png
Parallels can be drawn between Attestations and transaction confirmations on the Bitcoin timechain; however, their importance to you would be weighted by clients and/or Data Vending Machines in accordance with:
- Your social graph;
- The type or subject of the content being attested and by whom;
- Your personal preferences.
They could also have a validity duration to be temporally bound, which would be particularly useful in the case of Places.
NIP-25 (Reactions) do allow for users to up/downvote notes with optional content (e.g., emojis) and could work for Attestations, but I think we need something less ambiguous and more definitive.
‘This is true’ resonates more strongly than ‘I like this.’.
https://i.nostr.build/s8NIG2kXzUCLcoax.jpg
There are similar concepts in the Web 3 / Web 5 world such as Verified Credentials by tdb. However, Nostr is the Web 3 now and so wen Attestation NIP?
https://i.nostr.build/Cb047NWyHdJ7h5Ka.jpg
That said, I have seen @utxo has been exploring ‘smart contracts’ on nostr and Attestations may just be a relatively ‘dumb’ subset of the wider concept Nostr-native scripting combined with web-of-trust.
Proof of Place
Attestations handle the signalling of your truth, but what about the initial verification itself?
We already covered how this ultimately has to be derived from your social graph, but what if there was a way to help bootstrap this web-of-trust through the use of oracles? For those unfamiliar with oracles in the digital realm, they are simply trusted purveyors of truth.
Introducing Proof of Place, an out–of-band process where an oracle (such as BTC Map) would mail - yes physically mail- a shared secret to the address of the location being claimed in cyberspace. This shared secret would be locked to the public key (npub) making the claim, which, if unlocked, would prove that the associated private key (nsec) has physical access to the location in meatspace.
One way of doing this would be to mint a 1 sat cashu ecash token locked to the npub of the claimant and mail it to them. If they are able to redeem the token then they have cryptographically proven that they have physical access to the location.
Proof of Place is really nothing more than a weighted Attestation. In a web-of-trust Nostrverse, an oracle is simply a npub (say BTC Map) that you weigh heavily for its opinion on a given topic (say Places).
In the Bitcoin world, Proof of Work anchors digital scarcity in cyberspace to physical scarcity (energy and time) in meatspace and as @Gigi says in PoW is Essential:
"A failure to understand Proof of Work, is a failure to understand Bitcoin."
In the Nostrverse, Proof of Place helps bridge the digital and physical worlds.
@Gigi also observes in Memes vs The World that:
"In Bitcoin, the map is the territory. We can infer everything we care about by looking at the map alone."
https://i.nostr.build/dOnpxfI4u7EL2v4e.png
This isn’t true for Nostr.
In the Nostrverse, the map IS NOT the territory. However, Proof of Place enables us to send cryptographic drones down into the physical territory to help us interpret our digital maps. 🤯
Check-ins
Although not a draft NIP yet, @Arkinox has also been exploring the familiar concept of Foursquare-style Check-ins on Nostr (with kind 13811 notes).
For the uninitiated, Check-ins are simply notes that signal the publisher is at a given location. These locations could be Places (in the Nostr sense) or any other given digital representation of a location for that matter (such as OSM elements) if NIP-73 - External Content IDs are used.
Of course, not everyone will be a Check-in enjoyooor as the concept will not sit well with some people’s threat models and OpSec practices.
Bringing Check-ins to Nostr is possible (as @sebastix capably shows here), but they suffer the same authenticity issues as Places. Just because I say I'm at a given location doesn't mean that I am.
Back in the Web 2.0 days, Foursquare mitigated this by relying on the GPS position of the phone running their app, but this is of course spoofable.
How should we approach Check-in verifiability in the Nostrverse? Well, just like with Places, we can use Attestations and WoT. In the context of Check-ins, an Attestation from the identity (npub) of the Place being checked-in to would be a particularly strong signal. An NFC device could be placed in a coffee shop and attest to check-ins without requiring the owner to manually intervene - I’m sure @blackcoffee and @Ben Arc could hack something together over a weekend!
Check-ins could also be used as a signal for bonafide Place ownership over time.
Summary: Trust Your Bros
So, to recap, we have:
Places: Digital representations of physical locations on Nostr.
Check-ins: Users signalling their presence at a location.
Attestations: Verifiable social proofs used to confirm ownership or the truth of a claim.
You can visualise how these three concepts combine in the diagram below:
https://i.nostr.build/Uv2Jhx5BBfA51y0K.jpg
And, as always, top right trumps bottom left! We have:
Level 0 - Trust Me Bro: Anyone can check-in anywhere. The Place might not exist or might be impersonating the real place in meatspace. The person behind the npub may not have even been there at all.
Level 1 - Definitely Maybe Somewhere: This category covers the middle-ground of ‘Maybe at a Place’ and ‘Definitely Somewhere’. In these examples, you are either self-certifying that you have checked-in at an Attested Place or you are having others attest that you have checked-in at a Place that might not even exist IRL.
Level 2 - Trust Your Bros: An Attested Check-in at an Attested Place. Your individual level of trust would be a function of the number of Attestations and how you weigh them within your own social graph.
https://i.nostr.build/HtLAiJH1uQSTmdxf.jpg
Perhaps the gold standard (or should that be the Bitcoin standard?) would be a Check-in attested by the owner of the Place, which in itself was attested by BTC Map?
Or perhaps not. Ultimately, it’s the users responsibility to determine what they trust by forming their own perspective within the Nostrverse powered by web-of-trust algorithms they control. ‘Trust Me Bro’ or ‘Trust Your Bros’ - you decide.
As we navigate the frontier of cryptographic ownership and decentralised data, it’s up to us to find the balance between preserving the Open Data commons and embracing self-sovereign digital identities.
Thanks
With thanks to Arkinox, Avi, Ben Gunn, Kieran, Blackcoffee, Sebastix, Tomek, Calle, Short Fiat, Ben Weeks and Bitcoms for helping shape my thoughts and refine content, whether you know it or not!
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28The Lightning Network solves the problem of the decentralized commit
Before reading this, see Ripple and the problem of the decentralized commit.
The Bitcoin Lightning Network can be thought as a system similar to Ripple: there are conditional IOUs (HTLCs) that are sent in "prepare"-like messages across a route, and a secret
pthat must travel from the final receiver backwards through the route until it reaches the initial sender and possession of that secret serves to prove the payment as well as to make the IOU hold true.The difference is that if one of the parties don't send the "acknowledge" in time, the other has a trusted third-party with its own clock (that is the clock that is valid for everybody involved) to complain immediately at the timeout: the Bitcoin blockchain. If C has
pand B isn't acknowleding it, C tells the Bitcoin blockchain and it will force the transfer of the amount from B to C.Differences (or 1 upside and 3 downside)
-
The Lightning Network differs from a "pure" Ripple network in that when we send a "prepare" message on the Lightning Network, unlike on a pure Ripple network we're not just promising we will owe something -- instead we are putting the money on the table already for the other to get if we are not responsive.
-
The feature above removes the trust element from the equation. We can now have relationships with people we don't trust, as the Bitcoin blockchain will serve as an automated escrow for our conditional payments and no one will be harmed. Therefore it is much easier to build networks and route payments if you don't always require trust relationships.
-
However it introduces the cost of the capital. A ton of capital must be made available in channels and locked in HTLCs so payments can be routed. This leads to potential issues like the ones described in https://twitter.com/joostjgr/status/1308414364911841281.
-
Another issue that comes with the necessity of using the Bitcoin blockchain as an arbiter is that it may cost a lot in fees -- much more than the value of the payment that is being disputed -- to enforce it on the blockchain.[^closing-channels-for-nothing]
Solutions
Because the downsides listed above are so real and problematic -- and much more so when attacks from malicious peers are taken into account --, some have argued that the Lightning Network must rely on at least some trust between peers, which partly negate the benefit.
The introduction of purely trust-backend channels is the next step in the reasoning: if we are trusting already, why not make channels that don't touch the blockchain and don't require peers to commit large amounts of capital?
The reason is, again, the ambiguity that comes from the problem of the decentralized commit. Therefore hosted channels can be good when trust is required only from one side, like in the final hops of payments, but they cannot work in the middle of routes without eroding trust relationships between peers (however they can be useful if employed as channels between two nodes ran by the same person).
The next solution is a revamped pure Ripple network, one that solves the problem of the decentralized commit in a different way.
[^closing-channels-for-nothing]: That is even true when, for reasons of the payment being so small that it doesn't even deserve an actual HTLC that can be enforced on the chain (as per the protocol), even then the channel between the two nodes will be closed, only to make it very clear that there was a disagreement. Leaving it online would be harmful as one of the peers could repeat the attack again and again. This is a proof that ambiguity, in case of the pure Ripple network, is a very important issue.
-
-
 @ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23
@ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23由于gmail在中国被防火墙拦截了,无法打开,不想错过邮件通知。
通过自建ntfy接受gmail邮件通知。 怎么自建ntfy,后面再写。
2024年08月13日更新:
修改不通过添加邮件标签来标记已经发送的通知,通过Google Sheets来记录已经发送的通知。
为了不让Google Sheets文档的内容很多,导致文件变大,用脚本自动清理一个星期以前的数据。
准备工具
- Ntfy服务
- Google Script
- Google Sheets
操作步骤
- 在Ntfy后台账号,设置访问令牌。
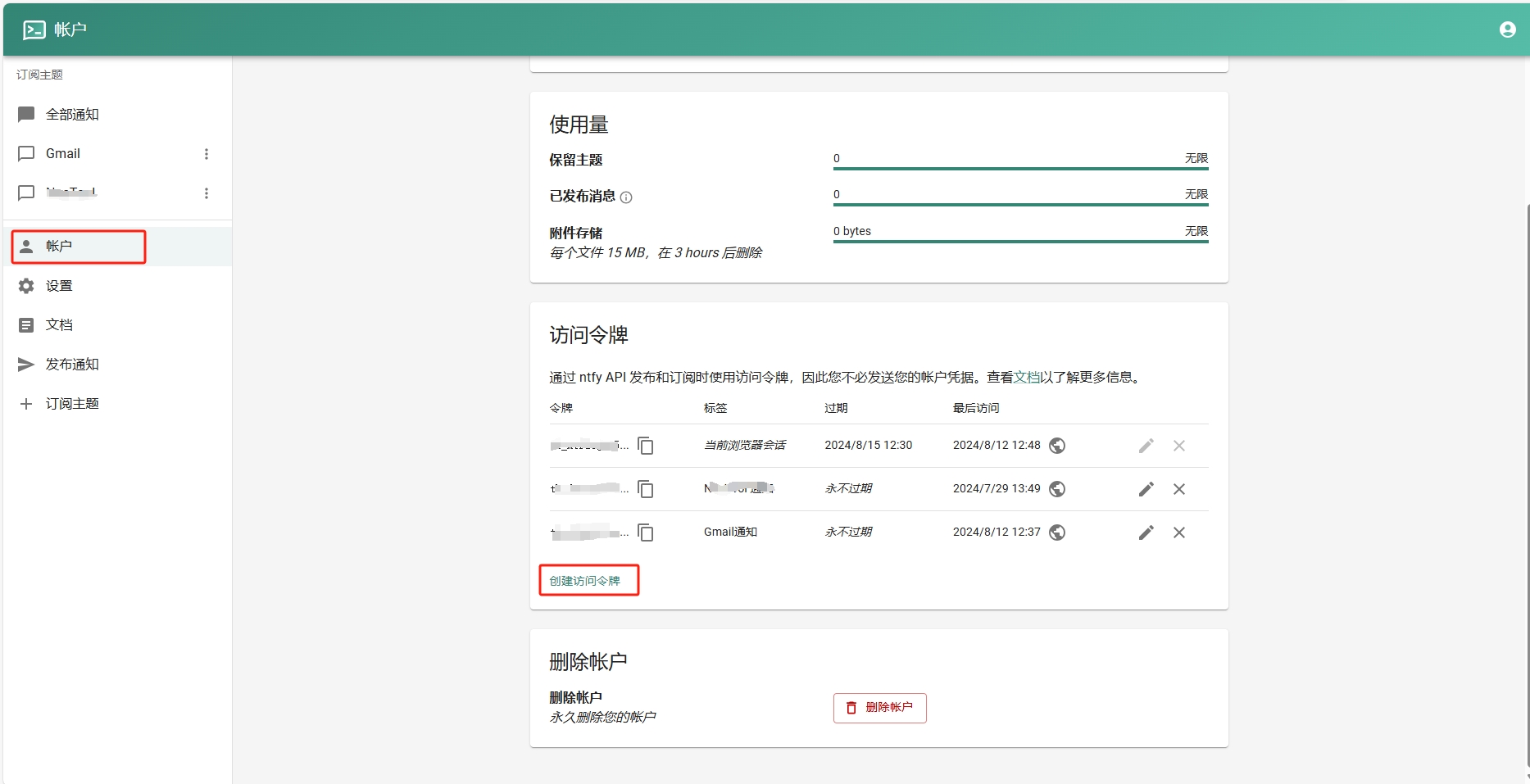
- 添加订阅主题。
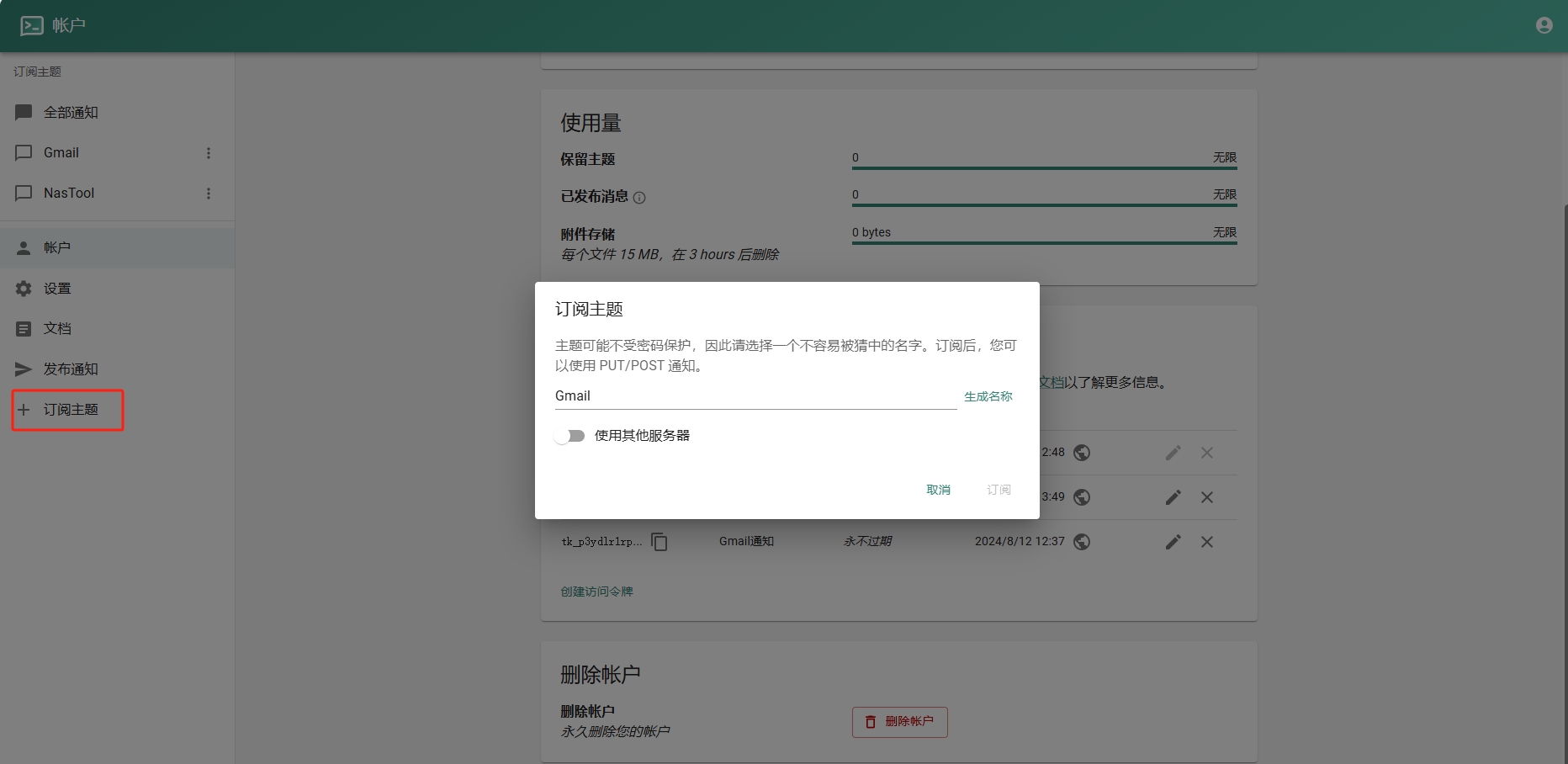
- 进入Google Sheets创建一个表格.记住id,如下图:
- 进入Google Script创建项目。填入以下代码(注意填入之前的ntfy地址和令牌):
```javascript function checkEmail() { var sheetId = "你的Google Sheets id"; // 替换为你的 Google Sheets ID var sheet = SpreadsheetApp.openById(sheetId).getActiveSheet();
// 清理一星期以前的数据 cleanOldData(sheet, 7 * 24 * 60); // 保留7天(即一周)内的数据
var sentEmails = getSentEmails(sheet);
var threads = GmailApp.search('is:unread'); Logger.log("Found threads: " + threads.length);
if (threads.length === 0) return;
threads.forEach(function(thread) { var threadId = thread.getId();
if (!sentEmails.includes(threadId)) { thread.getMessages().forEach(sendNtfyNotification); recordSentEmail(sheet, threadId); }}); }
function sendNtfyNotification(email) { if (!email) { Logger.log("Email object is undefined or null."); return; }
var message = `发件人: ${email.getFrom() || "未知发件人"} 主题: ${email.getSubject() || "无主题"}
内容: ${email.getPlainBody() || "无内容"}`;
var url = "https://你的ntfy地址/Gmail"; var options = { method: "post", payload: message, headers: { Authorization: "Bearer Ntfy的令牌" }, muteHttpExceptions: true };
try { var response = UrlFetchApp.fetch(url, options); Logger.log("Response: " + response.getContentText()); } catch (e) { Logger.log("Error: " + e.message); } }
function getSentEmails(sheet) { var data = sheet.getDataRange().getValues(); return data.map(row => row[0]); // Assuming email IDs are stored in the first column }
function recordSentEmail(sheet, threadId) { sheet.appendRow([threadId, new Date()]); }
function cleanOldData(sheet, minutes) { var now = new Date(); var thresholdDate = new Date(now.getTime() - minutes * 60 * 1000); // 获取X分钟前的时间
var data = sheet.getDataRange().getValues(); var rowsToDelete = [];
data.forEach(function(row, index) { var date = new Date(row[1]); // 假设日期保存在第二列 if (date < thresholdDate) { rowsToDelete.push(index + 1); // 存储要删除的行号 } });
// 逆序删除(从最后一行开始删除,以避免行号改变) rowsToDelete.reverse().forEach(function(row) { sheet.deleteRow(row); }); }
```
5.Google Script是有限制的不能频繁调用,可以设置五分钟调用一次。如图:
结尾
本人不会代码,以上代码都是通过chatgpt生成的。经过多次修改,刚开始会一直发送通知,后面修改后将已发送的通知放到一个“通知”的标签里。后续不会再次发送通知。
如需要发送通知后自动标记已读,可以把代码复制到chatgpt给你写。
-
 @ 3ffac3a6:2d656657
2024-12-22 02:16:45
@ 3ffac3a6:2d656657
2024-12-22 02:16:45In a small, quiet town nestled between rolling hills, there lived a boy named Ravi. Ravi was resourceful, hardworking, and had a knack for finding ways to support his family. His mother, a widow who worked tirelessly as a seamstress, inspired Ravi to pitch in wherever he could. His latest venture was ironing clothes for neighbors.
With his trusty old iron and a rickety wooden table, Ravi turned a small corner of their modest home into a makeshift laundry service. By day, he attended school and played with his friends, but in the evenings, he transformed into the “Iron Boy,” smoothing out wrinkles and earning a few precious coins.
One night, orders piled up after a local wedding had left everyone with wrinkled formalwear. Determined to finish, Ravi worked well past his usual bedtime. The warm glow of the lamp cast long shadows across the room as he focused on the rhythmic hiss of steam escaping the iron.
Just as the clock struck midnight, a soft clop-clop echoed from outside. Ravi froze, the iron hovering mid-air. The sound grew louder until it stopped right outside his window.
A deep, resonant voice broke the silence. “Didn’t your mother tell you not to be ironing clothes late at night?”
Ravi’s heart jumped into his throat. He turned slowly to the window, and his eyes widened. Standing there, framed by the moonlight, was a horse—a magnificent creature with a shimmering coat and a mane that seemed to ripple like liquid silver. Its dark eyes sparkled with an otherworldly light, and its lips moved as it spoke.
“W-who are you?” Ravi stammered, clutching the iron like a shield.
The horse tilted its head. “Names are not important. But you should know that ironing past midnight stirs things best left undisturbed.”
“Things? What things?” Ravi asked, his curiosity momentarily overriding his fear.
The horse snorted softly, a sound that almost resembled a chuckle. “Spirits. Shadows. Call them what you will. They grow restless in the heat of the iron at night. You don’t want to invite them in.”
Ravi glanced at the clothes piled on the table, then back at the horse. “But I need to finish these. People are counting on me.”
The horse’s eyes softened, and it stepped closer to the window. “Your dedication is admirable, but heed my warning. For tonight, let it be. Finish in the morning.”
Before Ravi could reply, the horse reared slightly, its silver mane glinting in the moonlight. With a final, cryptic look, it trotted off into the darkness, leaving Ravi staring after it in stunned silence.
The next morning, Ravi woke to find his mother standing at the table, finishing the last of the ironing. “You were so tired, I thought I’d help,” she said with a smile.
Ravi hesitated, then decided not to mention the midnight visitor. But from that day on, he made sure to finish his ironing before nightfall.
Though he never saw the horse again, he sometimes heard the faint clop-clop of hooves in the distance, as if reminding him of that strange, magical night. And in his heart, he carried the lesson that some tasks are best left for the light of day.
-
 @ 2063cd79:57bd1320
2025-01-02 12:56:08
@ 2063cd79:57bd1320
2025-01-02 12:56:08Bitcoin ist vieles. Bitcoin die Währung ist teilbar, austauschbar, einfach transportierbar, haltbar, prüfbar, knapp, universell akzeptiert und leicht sicherungsfähig. Bitcoin das Netzwerk ist staatenlos, dezentral, zensurresistent, erlaubnislos, diskriminiert nicht, vertrauenslos, pseudonym, open source, es basiert auf Konsens- und Anreizmechanismen und Verifizierung sowie Berechnung (wahrscheinlich habe ich sogar viele weitere Eigenschaften vergessen), aber ist Bitcoin auch wirklich unpolitisch, wie so oft behauptet?
Es wird häufig behauptet, dass Bitcoin unpolitisch sei. Aber was genau soll das bedeuten? Die einfachste Erklärung ist, dass Bitcoin für jeden frei zugänglich ist und von jedem benutzt werden kann, egal für welchen Zweck. In der Theorie auch für politische Zwecke, egal welcher Richtung. Bitcoin ist Politik in dieser Hinsicht egal. Denn das Bitcoin-Netzwerk richtet nicht, es diskriminiert nicht und es hat keine Meinung. Eine Transaktion ist eine Transaktion, egal wer der Urheber oder der Sender ist und egal, wer der Empfänger ist. Transaktionen müssen nicht gekennzeichnet werden und somit gibt es keine Möglichkeit für das Netzwerk zu entscheiden, ob eine Transaktion gut oder schlecht ist, dazu genutzt wird, um Guthaben von einer Wallet in eine andere zu schieben, oder von einem Land in ein anderes Land geschickt wird, um dort moralisch fragwürdige Motive zu unterstützen. Insofern ist Bitcoin unpolitisch: Das Netzwerk diskriminiert, oder besser gesagt beurteilt nicht aufgrund politischer Neigungen.
Aber dies ist eigentlich nur die Definition für die eingangs erwähnte Eigenschaft von Bitcoins Wertfreiheit (meiner Meinung nach eine bessere Ausdrucksweise für "Bitcoin diskriminiert nicht").
Aber Nichtdiskriminierung bzw. Wertfreiheit bedeutet nicht unbedingt unpolitisch oder apolitisch. Die Definition dieses Adjektivs bedeutet streng genommen:
[1] sich nicht für Politik interessierend, kein Interesse an politische Themen zeigend
[2] keine Steigerung: nicht die Politik betreffend, nicht zur Politik gehörend
Die erste Definition, da sind wir uns sicherlich einig, sollte erfüllt sein. Bitcoin interessiert sich nicht für Politik. Bitcoin ist ein Netzwerk, ein Protokoll, ein System. Bitcoin interessiert sich nur für sich selbst. Seinen eigenen Erhalt, und die im Protokoll festgesetzten Regeln: Etwa alle 10 Minuten wird ein neuer Block produziert, egal wie viel Rechenleistung dem Netzwerk zur Verfügung steht, egal wie viele Transaktionen hinzuzufügen sind, egal wie viele Netzwerkteilnehmer partizipieren.
Bei der zweiten Definition wird es allerdings etwas komplizierter. Bitcoin wurde von Satoshi als Peer-to-Peer Electronic Cash System ins Leben gerufen, das die inhärenten Schwächen des heutigen, vertrauensbasierten Modells löst. Satoshi identifizierte das Problem schon in 2009:
The root problem with conventional currency is all the trust that's required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust.
Der Genesis Block selbst enthält die wohl bekannteste aller Nachrichten, die jemals in der Bitcoin-Timechain verewigt wurden:
The Times 03/Jan/2009 Chancellor on brink of second bailout for banks
\ Damit ist die Konzeption und die Erschaffung des Bitcoin-Protokolls an sich schon ein politischer Akt. Bitcoin stellt eine Alternative zu unserem derzeitigen Geldsystem dar und soll oder könnte es, im besten Fall, sogar ersetzen. Bitcoin positioniert sich als Gegenstück zum Staat - dem derzeitigen Wächter und Herrn über das Geldsystem. Der Staat ist eine von Natur aus politische Instanz. Wenn man also mit etwas konkurriert, das dem Staat obliegt, wird es automatisch politisch. Satoshi selbst war zumindest indirekt vom Libertarismus und der österreichischen Ökonomie beeinflusst.
Das bedeutet keineswegs, dass jede Person, die Bitcoin verwendet, automatisch einem politischen Akt unterworfen wird, oder selbst anarchistische, libertäre oder liberale Ziele verfolgt. Allerdings bleibt nicht von der Hand zu weisen, dass Bitcoin und sein Ziel, eine Alternative zum heutigen vorherrschenden Geldsystem zu erschaffen, dadurch eine inhärent politische Bekundung ist.
Wenn Bitcoin also nicht apolitisch oder unpolitisch ist, aber auch nicht explizit politisch, dann könnte man behaupten Bitcoin sei zumindest anti-politisch. Der per Definition politische Staat und die Staatsgewalt über das Geldsystem sind der erklärte Gegenspieler von Bitcoin. Damit stellt sich Bitcoin als Kontrahent zu einem System auf, das die Gewalt in die Hände einiger Weniger legt. In der Politik gewinnen oder herrschen diejenigen, die die populärste Meinung vertreten (wenn es gut läuft), oder die meiste Gewalt hinter sich bündeln (wenn es nicht so gut läuft). Im Bitcoin-Netzwerk gewinnen diejenigen, die am effizientesten die Anreizstrukturen nutzen (Miner, Mining-Pools, Lightning-Routing-Channel Betreiber, etc.), oder Bitcoin am effizientesten für sich nutzen und damit dem Ökosystem zum Wachstum verhelfen (Unternehmer, Experten, Entwickler, etc.). Die politische Gesinnung dieser Netzwerkteilnehmer spielt dabei in erster Linie absolut keine Rolle. Es ist völlig egal, ob ein Node-Betreiber zu Hause Pickelhauben sammelt oder im Che Guevara T-Shirt Bitcoin-Protokolle schreibt.

Das heutige Geldsystem hat viele Nachteile, alle aufzuzählen würde den Rahmen sprengen, jedoch lassen sich einige prägnante leicht identifizieren: Rent-Seeking, des Bitcoiners liebstes Thema der Cantillon-Effekt, Geld- oder Münzentwertung und Geldmarktpolitik vereinen alle das gleiche zugrunde liegende Problem. Sie unterliegen alle der politischen Einflussnahme auf das System zum Vorteil einiger (privilegierter) Weniger. Denn was für die wenigen individuellen Vorteilsnehmer aussichtsreich und lohnenswert ist, ist für das Kollektiv schädlich und finanziell schädigend. Bitcoin stellt dazu die Alternative dar. Zwar lässt sich argumentieren, dass die vorhandene Menge und damit das Vermögen bereits heute ungerecht verteilt ist. Allerdings birgt diese Verteilung lediglich Vorteile für die Individuen, ohne jedoch das Kollektiv zu schädigen. Besitzer von großen Mengen bitcoin können genau so viel oder so wenig Einfluss auf das System nehmen, wie diejenigen, die verhältnismäßig wenig besitzen.

Wenn es irgendetwas von Wert gibt, ob Geld, Edelmetalle, oder sonstige Wertgegenstände, wird es auch immer Menschen geben, die davon mehr besitzen als andere - das ist ein unumstößlicher Fakt der Natur und auch Bitcoin wird daran nichts ändern können. Allerdings bietet Bitcoin die nötigen Anreizstrukturen, den eigenen Anteil zu vermehren. Wie schon erwähnt, werden Unternehmergeist, Expertenwissen und aufgebrachte Arbeit derjenigen, die das Netzwerk voranbringen, belohnt. Im Gegensatz zum aktuellen System, in dem oft nicht nur Unternehmergeist und Arbeitsleistung belohnt werden, sondern auch politische Einflussnahme, Prestige und Macht, oder sogar schon die Nähe und der Zugang zu diesen einflussreichen Interessengruppen. Korruption, Lobbyismus und politische Vorteilsnahme führen deshalb zu unproduktiver Arbeit, bei der einzig und allein der Begünstigte profitiert.

Bitcoin eliminiert diese politische Vorteilsnahme und ist dadurch schon anti-politisch.
In diesem Sinne ist Bitcoin also politisch, wie alles politisch ist oder zu einem politischen Thema gemacht werden kann. Ich habe in einem früheren Artikel bereits beschrieben, dass der Staat für viele Menschen die Rolle einer Art Religion eingenommen hat und dass Bitcoin in gewisser Weise für den Staat das ist, was der Buchdruck damals für Religion war.
https://www.genexyz.org/post/13-block-754250-die-vollst-ndige-adaption-von-bitcoin-und-die-3-hindernisse-74u3k2/
Religion ist eigentlich unpolitisch, obwohl man behaupten darf, dass Kirchgänger gewisser Religionen im Allgemeinen im gleichen Bereich des politischen Spektrums wiederzufinden sind, macht dies Religion nicht von Natur aus politisch. Doch die Trennung von Kirche und Staat kann wohl als hochpolitisch bezeichnet werden.
Wo Diderot, Rousseau und Voltaire eine Berufung auf die Vernunft als universelle Urteilsinstanz propagierten und einen Kampf gegen Vorurteile und für die Hinwendung zu Naturwissenschaften, religiöse Toleranz und eine Orientierung am Naturrecht einleiteten, streben Bitcoin und seine Befürworter eine Abkehr von den staatlich gesteuerten und (Fiskal- und Geld)politisch aufgeladenen Finanz- und Wirtschaftsinterventionen und eine Berufung auf Werte wie Dezentralität, Zensurresistenz und Selbstbestimmtheit an. Dasselbe gilt für die Trennung von Geld und Staat. Geld ist eigentlich unpolitisch, aber die Trennung von Geld und Staat ist hochpolitisch. Auch der Missbrauch von Geld zum Erreichen von politischen Zielen ist hochpolitisch. Wie eingangs erwähnt, wird Bitcoin so politisiert - nur eben als Gegenentwurf. Als anti-politische Alternative zum politischen Fiat-System mit all seinen Fehlern.

Was ich damit sagen will, ist, dass Bitcoin per se politisch ist. Es ist eben nur ein anderer Entwurf zu dem politischen Denken, das heute vorherrscht. Bitcoin ist und bleibt erlaubnislos und wertfrei, damit ist die Nutzung von Bitcoin erstmal im Generellen unpolitisch. Solange bis auch einzelne Anwendungsfälle von politischer Natur sind. Bitcoin-Spenden an Wikileaks haben eine politische Tragweite. Bitcoin-Spenden an den Freedom-Convoy in Kanada sind politisch. Bitcoin-Spenden an Hodlonaut sind politisch, auch wenn es dabei um die hauseigene Politik im Bitcoin-Ökosystem geht.
Man kann also nicht ohne weiteres sagen "Bitcoin ist unpolitisch". Es ist richtiger zu sagen, dass Bitcoin keine politische Meinung vertritt und sich nicht zu politischer Einflussnahme instrumentalisieren lässt. Bitcoin ist ein Protokoll, ein Netzwerk, und kümmert sich nur um sich selbst. Aber Bitcoin ist sehr wohl politisch.
🫳🎤
In diesem Sinne, 2... 1... Risiko!
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Webvatar
Like Gravatar, but using profile images from websites tagged with "microformats-2" tags, like people from the indiewebcamp movement liked. It falled back to favicon, gravatar and procedural avatar generators.
No one really used this, despite people saying they liked it. Since I was desperate to getting some of my programs appreciated by someone I even bought a domain. It was sad, but an enriching experience.
See also
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Eltoo
Read the paper, it's actually nice and small. You can read only everything up to section 4.2 and it will be enough. Done.
Ok, you don't want to. Or you tried but still want to read here.
Eltoo is a way of keeping payment channel state that works better than the original scheme used in Lightning. Since Lightning is a bunch of different protocols glued together, it can It replace just the part the previously dealed with keeping the payment channel.
Eltoo works like this: A and B want a payment channel, so they create a multisig transaction with deposits from both -- or from just one, doesn't matter. That transaction is only spendable if both cooperate. So if one of them is unresponsive or non-cooperative the other must have a way to get his funds back, so they also create an update transaction but don't publish it to the blockchain. That update transaction spends to a settlement transaction that then distributes the money back to A and B as their balances say.
If they are cooperative they can change the balances of the channel by just creating new update transactions and settlement transactions and number them like 1, 2, 3, 4 etc.

Solid arrows means a transaction is presigned to spend only that previous other transaction; dotted arrows mean it's a floating transaction that can spend any of the previous.
Why do they need and update and a settlement transaction?
Because if B publishes update2 (in which his balances were greater) A needs some time to publish update4 (the latest, which holds correct state of balances).
Each update transaction can be spent by any newer update transaction immediately or by its own specific settlement transaction only after some time -- or some blocks.
Hopefully you got that.
How do they close the channel?
If they're cooperative they can just agree to spend the funding transaction, that first multisig transaction I mentioned, to whatever destinations they want. If one party isn't cooperating the other can just publish the latest update transaction, wait a while, then publish its settlement transaction.
How is this better than the previous way of keeping channel states?
Eltoo is better because nodes only have to keep the last set of update and settlement transactions. Before they had to keep all intermediate state updates.
If it is so better why didn't they do it first?
Because they didn't have the idea. And also because they needed an update to the Bitcoin protocol that allowed the presigned update transactions to spend any of the previous update transactions. This protocol update is called
SIGHASH_NOINPUT[^anyprevout], you've seen this name out there. By marking a transaction withSIGHASH_NOINPUTit enters a mystical state and becomes a floating transaction that can be bound to any other transaction as long as its unlocking script matches the locking script.Why can't update2 bind itself to update4 and spend that?
Good question. It can. But then it can't anymore, because Eltoo uses
OP_CHECKLOCKTIMEVERIFYto ensure that doesn't actually check not a locktime, but a sequence. It's all arcane stuff.And then Eltoo update transactions are numbered and their lock/unlock scripts will only match if a transaction is being spent by another one that's greater than it.
Do Eltoo channels expire?
No.
What is that "on-chain protocol" they talk about in the paper?
That's just an example to guide you through how the off-chain protocol works. Read carefully or don't read it at all. The off-chain mechanics is different from the on-chain mechanics. Repeating: the on-chain protocol is useless in the real world, it's just a didactic tool.
[^anyprevout]: Later
SIGHASH_NOINPUTwas modified to fit better with Taproot and Schnorr signatures and renamed toSIGHASH_ANYPREVOUT. -
 @ 58937958:545e6994
2025-01-02 12:33:17
@ 58937958:545e6994
2025-01-02 12:33:17May 22, 2024 I made Badger-kun’s pizza bread to celebrate Bitcoin Pizza Day.
Badger-kun: A character from the Japanese YouTube channel "Bitcoiner Hanseikai."
Making the pizza bread was quite a challenge:
Attempt 1: Rice Flour Bread
I thought it might be difficult to shape the character using yeast-based dough (since fermentation might turn it into just a plain round shape). So, I tried rice flour bread with psyllium, but it didn’t feel quite right.
Attempt 2: Cream Bread Style
The rice flour bread was too firm, so I wanted to try something softer. It ended up burning.
Attempt 3: Cheese Naan Style
 I wanted to capture that melty cheese vibe and finally thought of cheese naan.
For a character-themed pizza bread, this cheese naan approach seemed to work pretty well.
I realized that simpler character designs might be easier (and clearer) to make.
nostr:nevent1qqsd3a7thkzqde4sp4hx7qjwrjp4kxsnl66kytx40mk73djfvxfkspgu2fw34
I wanted to capture that melty cheese vibe and finally thought of cheese naan.
For a character-themed pizza bread, this cheese naan approach seemed to work pretty well.
I realized that simpler character designs might be easier (and clearer) to make.
nostr:nevent1qqsd3a7thkzqde4sp4hx7qjwrjp4kxsnl66kytx40mk73djfvxfkspgu2fw34 -
 @ eac63075:b4988b48
2024-12-18 11:35:25
@ eac63075:b4988b48
2024-12-18 11:35:25The European Union is at a crossroads. While digital innovation and security cooperation remain critical in a connected world, recent proposals to enhance police surveillance and data sharing are stirring deep concerns about individual privacy, data security, and democratic oversight. Two recent reports published by Statewatch shed light on troubling developments in the EU’s policing landscape, raising alarms among privacy advocates and civil rights organizations.
The EU’s new plans to expand police surveillance could put your privacy and rights at risk and introduce risks far outweighing their potential benefits. This article will analyze these proposals, their implications, and the growing opposition from privacy and civil liberties defenders.
Surveillance Infrastructure: Policing by Design
The first Statewatch report, titled “Policing by Design: The Latest EU Surveillance Plan”, outlines a concerning trend in the EU’s approach to law enforcement. The proposals advocate embedding surveillance tools directly into the design of new technologies, effectively creating an architecture where policing capabilities are integrated into the systems we use daily.
From facial recognition cameras to AI-driven analytics, the EU plans to enhance cross-border police cooperation by ensuring technology is designed to facilitate surveillance from the outset. Known as “policing by design,” this strategy involves building surveillance features directly into technologies we use every day. Imagine a network of cameras or software that can automatically monitor people’s faces or behaviors without any extra installation — it’s like your everyday tech quietly doubling as a police tool. The goal is to enable seamless sharing of data across borders for criminal investigations, but the unintended consequences are alarming.
The Problem with “Policing by Design”
- Mass Surveillance Normalized: By embedding surveillance features into public and private infrastructure, society risks normalizing mass surveillance, where every movement, transaction, or online interaction is monitored and analyzed.
- Threats to Privacy: Such initiatives inherently contradict the principle of privacy by design, which prioritizes privacy protections in the development of technology. Instead, citizens are being treated as subjects of perpetual suspicion.
- Lack of Transparency and Accountability: A systemic lack of transparency surrounding these plans raises serious governance issues. Civil society organizations, journalists, and privacy advocates have pointed to a lack of democratic oversight and meaningful debate.
- Risks of Abuse: Surveillance systems are often deployed under the guise of security but are susceptible to abuse. History shows that tools designed for law enforcement can easily be turned against dissenters, journalists, or marginalized communities.
As the report highlights, these developments could establish a permanent surveillance infrastructure across Europe, enabling the collection of biometric, behavioral, and communications data on an unprecedented scale.
Flawed Justifications for Surveillance Expansion
Privacy advocacy organizations, including the European Digital Rights (EDRi) network, argue that much of the justification for these surveillance plans relies on flawed assumptions. The rhetoric of the “Going Dark” report, which claims that law enforcement is losing access to communications due to encryption, has been widely debunked. As EDRi points out, law enforcement already has extensive tools at their disposal to access data and track individuals, but the focus on encryption risks undermining secure communication for everyone.
Instead of addressing systemic issues within law enforcement, these flawed reports have fueled calls for intrusive surveillance systems that risk eroding privacy while offering little evidence of improving public safety.
Centralized Police Data: A Substantial Security and Privacy Threat
A second Statewatch report, titled “EU Police Data Plans Pose Substantial Security and Privacy Threats”, explores another equally concerning initiative: the EU’s push to centralize police data repositories and expand their use.
The EU has already established several large-scale databases, such as the Schengen Information System (SIS), which stores data about individuals who may be denied entry into the EU, and the Europol Information System, which can hold details about millions of people, including those not suspected of crimes. For example, a traveler flagged mistakenly in the system could face unnecessary scrutiny, detention, or restrictions when crossing borders — highlighting the real-world risks of inaccurate or overreaching data collection. The new proposals aim to go further, creating an interoperable web of police data accessible to law enforcement agencies across member states. Proponents argue this is necessary for combating cross-border crime and terrorism, but the risks are immense.
Key Concerns with Centralized Police Data
- Massive Data Collection: The EU’s proposed systems would require the collection of highly sensitive data, including biometric information (fingerprints, facial recognition scans) and behavioral analytics, to track individuals’ activities across borders.
- Data Misuse and Security Risks: Centralized data systems are prime targets for cyberattacks, data breaches, and misuse. The larger and more interconnected the system, the greater the risks of unauthorized access, theft, or corruption of the data.
- As Statewatch points out, the systems lack robust safeguards to prevent misuse or to ensure that data is handled proportionately and lawfully.
- Erosion of Trust in Law Enforcement: Building centralized data repositories without meaningful safeguards undermines public trust. Individuals may be less willing to engage with law enforcement if they fear their data will be stored indefinitely, shared across borders, or used inappropriately.
- Impact on Fundamental Rights: Mass police databases can violate the principle of proportionality, a cornerstone of EU law. By collecting and sharing data indiscriminately, these systems erode fundamental rights, including the right to privacy, freedom of movement, and the presumption of innocence.
Civil Society Opposition and Democratic Accountability
In an open letter to EU institutions, over 30 civil society organizations — including EDRi — have criticized the lack of transparency in the High-Level Group’s (HLG) recommendations for data access. The letter highlights a concerning pattern: while industry stakeholders are included in key discussions, civil society voices remain sidelined. This exclusion undermines democratic accountability and reinforces fears that surveillance policies are being driven by corporate interests rather than public well-being.
These organizations have called for the EU to prioritize transparency, include meaningful public debate, and ensure any law enforcement proposals respect proportionality and fundamental rights.
Why Privacy Advocates Are Sounding the Alarm
The reports from Statewatch highlight a fundamental clash between security policy and individual rights. Privacy advocates are urging EU lawmakers to take a step back and critically examine the following issues:
- Lack of Democratic Oversight: Proposals to integrate surveillance systems and expand police databases are being pushed forward without genuine public debate or oversight. Civil society organizations have been excluded from key discussions.
- Failure to Uphold Privacy Laws: The EU has some of the strongest privacy laws in the world, including the General Data Protection Regulation (GDPR). However, these proposals risk undermining GDPR principles by enabling indiscriminate data collection and sharing.
- Ignoring Proportionality: Surveillance systems must be targeted, necessary, and proportionate to their objectives. Embedding policing into technological design and centralizing data far exceeds what is justified for fighting crime and terrorism.
- Setting Dangerous Precedents: The failure to fully ban harmful surveillance technologies like facial recognition in public spaces sets a troubling precedent. It risks not only eroding privacy within the EU but also encouraging other nations to adopt similar measures, undermining global human rights.
A Call for Action: Safeguarding Our Privacy and Rights
As the EU pushes forward with these plans, the opposition from civil rights defenders grows louder. Policymakers must address the following key demands to prevent an erosion of fundamental rights:
- Implement Privacy by Design: All new technologies must prioritize privacy protections at the design stage, ensuring they are not co-opted for surveillance.
- Establish Robust Oversight: Any new policing tools or databases must be subject to democratic scrutiny, independent oversight, and clear legal frameworks to prevent misuse.
- Reassess Interoperability Plans: Cross-border police cooperation is important, but it must not come at the cost of individuals’ privacy, security, and dignity.
- Strengthen Export Controls: The EU must ban the export of surveillance tools that risk facilitating human rights abuses in authoritarian regimes.
- Prioritize Data Security: Centralized systems require state-of-the-art security measures to protect sensitive data from breaches or misuse.
The EU’s role as a leader in digital rights and privacy is now at stake. If these plans proceed without significant safeguards, Europe risks undermining its own foundational principles of freedom, security, and justice.
Conclusion: The Price of Surveillance-Driven Security
The EU’s surveillance plans may be presented as necessary for security, but they come at a steep cost to privacy, trust, and individual freedoms. Embedding surveillance into our technologies and centralizing police data pose far-reaching risks that cannot be ignored.
As privacy advocates, it is our responsibility to hold policymakers accountable and demand a security framework that upholds, rather than undermines, fundamental rights. Europe’s future must not be built on surveillance by design — but on privacy, democracy, and trust.
-
 @ ac8bb9b0:70278acc
2024-12-04 20:30:30
@ ac8bb9b0:70278acc
2024-12-04 20:30:30Chef's notes
Make Ahead: You can prepare this recipe up to one week in advance. Store it in an airtight container in the refrigerator.
To Freeze: Allow the dish to cool completely before transferring it to a freezer-safe bag. Lay the bag flat in the freezer to ensure even freezing and to save space. Thaw it in the refrigerator overnight before using it.
Details
- ⏲️ Prep time: 5
- 🍳 Cook time: 5
- 🍽️ Servings: 1
Ingredients
- ½ cup soy sauce
- 2 Tablespoons rice vinegar
- 1 Tablespoon sesame oil
- 1/4 cup + 1 Tablespoon light brown sugar
- 1 Tablespoon honey
- 3/4 teaspoon ground ginger
- 1 clove garlic , minced
- 2 teaspoons cornstarch+ 2 tsp water , mixed together to make a cornstarch slurry
- 1/4 teaspoon crushed red pepper flakes
Directions
- Make the teriyaki sauce by adding all of the sauce ingredients to a small saucepan over medium heat.
- Bring to a boil, stirring constantly, and boil for about 1 minute. The sauce should be thick enough to coat the back of the spoon.
- Serve over rice or with a stir-fry. See post above for additional ideas.
-
 @ 58937958:545e6994
2025-01-02 12:32:51
@ 58937958:545e6994
2025-01-02 12:32:512024年5月22日
ビットコイン・ピザ・デーに合わせてバッジャー君のピザパンを作りました
バッジャー君…日本のYoutubeチャンネル「ビットコイナー反省会」のキャラクター
ピザパン作りはかなり苦戦しました
1回目:米粉パン
イースト発酵だとキャラクターの形を作りにくい気がして(作っても発酵後に単なる丸になっちゃう懸念)
サイリウムを使った米粉パンにしたんですけど
何かこれじゃない感
2回目:クリームパン風
米粉パンが固かったので柔らかいパンが食べたくなりました
焦げました
3回目:チーズナン風
 とろけるチーズ感を出したいな~と考えて
とろけるチーズ感を出したいな~と考えてここでようやくチーズナンを思いつく
キャラクター×ピザパンならこのチーズナン方式が結構いいかもしれない
もうちょっとシンプルなキャラクターだと作りやすそう(分かりやすそう)だと思いました nostr:nevent1qqsd3a7thkzqde4sp4hx7qjwrjp4kxsnl66kytx40mk73djfvxfkspgu2fw34
-
 @ 58937958:545e6994
2025-01-02 12:32:28
@ 58937958:545e6994
2025-01-02 12:32:28October 31, 2024 I made pumpkin yokan to celebrate the anniversary of the Bitcoin whitepaper release.
*Yokan: A firm, jelly-like Japanese dessert typically made with azuki bean paste.
Cut a clear file into the shape of the Bitcoin logo.
 Place the ₿ mark on a slightly firm milk jelly (gyunyukan) and carefully cut it out with a knife.
Place the ₿ mark on a slightly firm milk jelly (gyunyukan) and carefully cut it out with a knife. Fill the cut-out with pumpkin yokan.
Fill the cut-out with pumpkin yokan.The mixture I made was a bit firm, so it was challenging to fill the gaps in the ₿ shape. Later, I tried a milk-based yokan with a smoother texture, which made the process much easier.
nostr:nevent1qqszzcz9npq5xgw08tp5wud0kg9wfacf9fkj07gu82wn3wjsad3wd2cppvjdw
You don’t need any special molds, so anyone can try this! I’m thinking of experimenting with different variations of the milk jelly and applying this technique to other dishes as well.
-
 @ fe32298e:20516265
2024-12-16 20:59:13
@ fe32298e:20516265
2024-12-16 20:59:13Today I learned how to install NVapi to monitor my GPUs in Home Assistant.
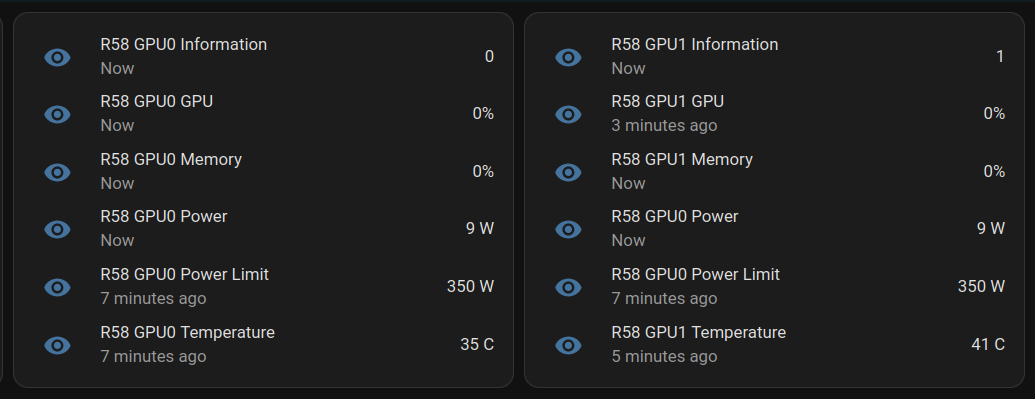
NVApi is a lightweight API designed for monitoring NVIDIA GPU utilization and enabling automated power management. It provides real-time GPU metrics, supports integration with tools like Home Assistant, and offers flexible power management and PCIe link speed management based on workload and thermal conditions.
- GPU Utilization Monitoring: Utilization, memory usage, temperature, fan speed, and power consumption.
- Automated Power Limiting: Adjusts power limits dynamically based on temperature thresholds and total power caps, configurable per GPU or globally.
- Cross-GPU Coordination: Total power budget applies across multiple GPUs in the same system.
- PCIe Link Speed Management: Controls minimum and maximum PCIe link speeds with idle thresholds for power optimization.
- Home Assistant Integration: Uses the built-in RESTful platform and template sensors.
Getting the Data
sudo apt install golang-go git clone https://github.com/sammcj/NVApi.git cd NVapi go run main.go -port 9999 -rate 1 curl http://localhost:9999/gpuResponse for a single GPU:
[ { "index": 0, "name": "NVIDIA GeForce RTX 4090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 16, "power_limit_watts": 450, "memory_total_gb": 23.99, "memory_used_gb": 0.46, "memory_free_gb": 23.52, "memory_usage_percent": 2, "temperature": 38, "processes": [], "pcie_link_state": "not managed" } ]Response for multiple GPUs:
[ { "index": 0, "name": "NVIDIA GeForce RTX 3090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 14, "power_limit_watts": 350, "memory_total_gb": 24, "memory_used_gb": 0.43, "memory_free_gb": 23.57, "memory_usage_percent": 2, "temperature": 36, "processes": [], "pcie_link_state": "not managed" }, { "index": 1, "name": "NVIDIA RTX A4000", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 10, "power_limit_watts": 140, "memory_total_gb": 15.99, "memory_used_gb": 0.56, "memory_free_gb": 15.43, "memory_usage_percent": 3, "temperature": 41, "processes": [], "pcie_link_state": "not managed" } ]Start at Boot
Create
/etc/systemd/system/nvapi.service:``` [Unit] Description=Run NVapi After=network.target
[Service] Type=simple Environment="GOPATH=/home/ansible/go" WorkingDirectory=/home/ansible/NVapi ExecStart=/usr/bin/go run main.go -port 9999 -rate 1 Restart=always User=ansible
Environment="GPU_TEMP_CHECK_INTERVAL=5"
Environment="GPU_TOTAL_POWER_CAP=400"
Environment="GPU_0_LOW_TEMP=40"
Environment="GPU_0_MEDIUM_TEMP=70"
Environment="GPU_0_LOW_TEMP_LIMIT=135"
Environment="GPU_0_MEDIUM_TEMP_LIMIT=120"
Environment="GPU_0_HIGH_TEMP_LIMIT=100"
Environment="GPU_1_LOW_TEMP=45"
Environment="GPU_1_MEDIUM_TEMP=75"
Environment="GPU_1_LOW_TEMP_LIMIT=140"
Environment="GPU_1_MEDIUM_TEMP_LIMIT=125"
Environment="GPU_1_HIGH_TEMP_LIMIT=110"
[Install] WantedBy=multi-user.target ```
Home Assistant
Add to Home Assistant
configuration.yamland restart HA (completely).For a single GPU, this works: ``` sensor: - platform: rest name: MYPC GPU Information resource: http://mypc:9999 method: GET headers: Content-Type: application/json value_template: "{{ value_json[0].index }}" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature scan_interval: 1 # seconds
- platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} GPU" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Memory" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Temperature" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'temperature') }}" unit_of_measurement: "°C" ```
For multiple GPUs: ``` rest: scan_interval: 1 resource: http://mypc:9999 sensor: - name: "MYPC GPU0 Information" value_template: "{{ value_json[0].index }}" json_attributes_path: "$.0" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature - name: "MYPC GPU1 Information" value_template: "{{ value_json[1].index }}" json_attributes_path: "$.1" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature
-
platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC GPU0 GPU" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC GPU0 Memory" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC GPU0 Power" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC GPU0 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC GPU0 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'temperature') }}" unit_of_measurement: "C"
-
platform: template sensors: mypc_gpu_1_gpu: friendly_name: "MYPC GPU1 GPU" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_memory: friendly_name: "MYPC GPU1 Memory" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_power: friendly_name: "MYPC GPU1 Power" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_1_power_limit: friendly_name: "MYPC GPU1 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_1_temperature: friendly_name: "MYPC GPU1 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'temperature') }}" unit_of_measurement: "C"
```
Basic entity card:
type: entities entities: - entity: sensor.mypc_gpu_0_gpu secondary_info: last-updated - entity: sensor.mypc_gpu_0_memory secondary_info: last-updated - entity: sensor.mypc_gpu_0_power secondary_info: last-updated - entity: sensor.mypc_gpu_0_power_limit secondary_info: last-updated - entity: sensor.mypc_gpu_0_temperature secondary_info: last-updatedAnsible Role
```
-
name: install go become: true package: name: golang-go state: present
-
name: git clone git: repo: "https://github.com/sammcj/NVApi.git" dest: "/home/ansible/NVapi" update: yes force: true
go run main.go -port 9999 -rate 1
-
name: install systemd service become: true copy: src: nvapi.service dest: /etc/systemd/system/nvapi.service
-
name: Reload systemd daemons, enable, and restart nvapi become: true systemd: name: nvapi daemon_reload: yes enabled: yes state: restarted ```