-

@ 7d33ba57:1b82db35
2025-02-14 01:46:37
The short answer is YES—but the more honest answer is that it’s much harder than when I started. I’ve been in the travel stock media industry for over 13 years, creating a vast archive of stock photos and videos from around the world. You can check out my portfolio on [https://www.shutterstock.com/g/traveltelly](Shutterstock).
My work is also available on Pond5, Videoblocks, and Adobe Stock. Other big agencies where I don’t have my media are Getty Images and iStock.
My media has been featured on TV channels and even in feature films. However, most of the time, contributors don’t know exactly where their content is used—stock agencies (the middlemen) keep that information to themselves. While stock media can still generate income, it requires persistence, a large portfolio, and an understanding of the ever-changing market.
When I started filming stock footage, most people didn’t even have a phone capable of taking good photos or videos—can you imagine? Now, everyone is a (travel) content creator. Technology has evolved, but creating a well-composed photo or video is still an art. However, the combination of improved tech and the increasing centralization of the stock media market has made it much harder to earn a decent income from stock media compared to 10 years ago.

**Centralization & Declining Royalties**
Over the years, I’ve watched stock media royalties decline year after year. In the beginning, I couldn't understand why I wasn’t able to recoup the cost of my expensive camera—one I specifically bought to shoot high-quality 4K footage.
As the stock media industry became more centralized, agencies took a larger cut while contributors earned less, despite creating higher-quality content. The market became saturated, and with more competition and lower payouts, making a sustainable income from stock media became increasingly difficult.

**The Reality of Centralization in Stock Media**
Every year, stock agencies announced yet another royalty downgrade for contributors. They always framed it as something beneficial for content creators, but in reality, it only served the big companies and their shareholders.
As content creators, we had no say in the matter. These agencies grew too big and powerful, and they knew it. Leaving one platform wasn’t really an option—doing so would only mean an even greater loss of income.
In recent years, the industry has become even more centralized, with only a handful of major agencies buying out smaller competitors. This consolidation further reduces competition, giving contributors even less control over pricing, royalties, and where their content is used.

**The Bitcoin Standard: A Wake-Up Call**
I couldn’t understand why I was struggling to pay off my expensive camera investment, despite working hard and producing high-quality content. Until then, I had never really thought about how money worked. That changed in 2018 when I read The Bitcoin Standard—an absolute eye-opener.
That book sparked my curiosity about Bitcoin. Like many, I initially got distracted by shitcoins, thinking I could multiply my holdings faster—after all, Bitcoin seemed “too expensive.” It was a hard but valuable lesson. Just like in a casino, you can win and lose a lot with altcoins, but that has nothing to do with Bitcoin itself. After those first few years of learning, I realized that for me, Bitcoin—not crypto—was the only way forward.

**From Centralization to Decentralization**
When people ask me if they should start selling stock footage, my answer is always the same: It’s much harder now than when I started. Sure, you can make a few bucks, but is all the time and effort really worth it? If I had to start today, I simply wouldn’t—it’s way more work than what you’ll earn.
Instead of spending years building content for centralized platforms that take the biggest cut, I believe it’s better to focus on decentralized media like Nostr. In my opinion, that’s where the future lies.

Nostr: A New Protocol for Socializing (and More)
Nostr is a revolutionary protocol that goes beyond just social networking. You can read all about it at [Nostr.org](Nostr.org).
As a content creator, one of the most exciting aspects of Nostr is the ability to earn directly through Zaps—small payments made in Satoshis (the smallest unit of Bitcoin).
* 1 Bitcoin = 100 million Satoshis
* By receiving Zaps, you’re not just earning—you’re stacking the hardest money (Bitcoin) directly on Nostr.
This shift toward decentralized earning is a game changer, giving creators more control and financial sovereignty compared to traditional, centralized platforms.

**Join Nostr and Create Your Freedom Content**
On Nostr, no one can stop you. No one can deplatform you. You can be truly free.Whether you're a content creator, artist, or thinker, Nostr empowers you to share your work without censorship or gatekeepers. It’s a place where you control your content, connect directly with your audience, and even earn Bitcoin through Zaps.Embrace decentralization.
***Join Nostr and take back your freedom*** 🚀
-

@ 85bdb587:7339d672
2025-02-13 22:56:08
## Marty's Bent
I must admit, I have been thoroughly impressed with the work the Trump administration has done since taking the reins from the Biden admin 23 days ago. Over the course of the first eight years of this newsletter there were multiple books-worth of words written about the rampant government corruption in the United States and the negative effects it was having on the economy, freedom and the psyche of the American people. The emergence of DOGE, its rag-tag team of autistic Gen Z'ers and the blatant fraud that has been surfaced is equally gratifying and infuriating.
For the longest time any American taxpayer with the smallest shred of common sense has known that they've been getting screwed by the federal government. We've said it for many years; taxes are a humiliation ritual in which the Common Man works his ass off for a meager wage, the government takes one third of it, and then lines their own pockets. We were reaching levels of corruption that rivaled Soviet Russia.
*“We know that they are lying, they know that they are lying, they even know that we know they are lying, we also know that they know we know they are lying too, they of course know that we certainly know they know we know they are lying too as well, but they are still lying. In our country, the lie has become not just moral category, but the pillar industry of this country.”* - Aleksandr Solzhenitsyn
The fact that all of the corruption that has been building up for decades in the United States is being brought to the light is extremely encouraging. We're not out of the woods yet, but it looks like we're actually making material progress to unveil the parasites in Washington DC. Hopefully DOGE's actions will lead to their eradication from American politics and a shrinking of the federal government to its smallest viable form. Nothing proves that DOGE is over the target more than the pearl clutching and screeching that is coming from the halls of Congress. FEED ME the crocodile tears of Elizabeth Warren, Maxine Waters and Mitch McConnell. These people are criminals and deserve nothing but the utmost contempt from the American people. The louder the screams coming from these individuals and others in similar positions should only be seen as confirmation that they are scared and are attempting to evade justice by screaming "CoNsTiTuTiOnAl CrIsIs" as many times as is humanly possible.
With all of that being said, DOGE should be seen as a mechanism to identify corruption, root it out, and salvage what they can of the American taxpayers' money. It's an admirable endeavor that should be lauded, but it only goes so far. Unfortunately for the United States, you can't DOGE the debt. via TFTC
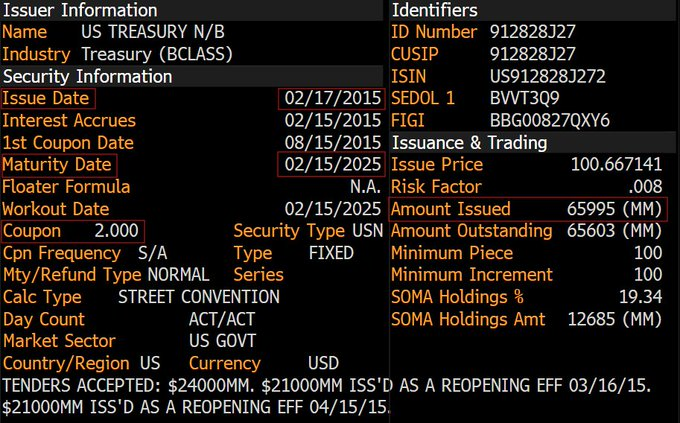
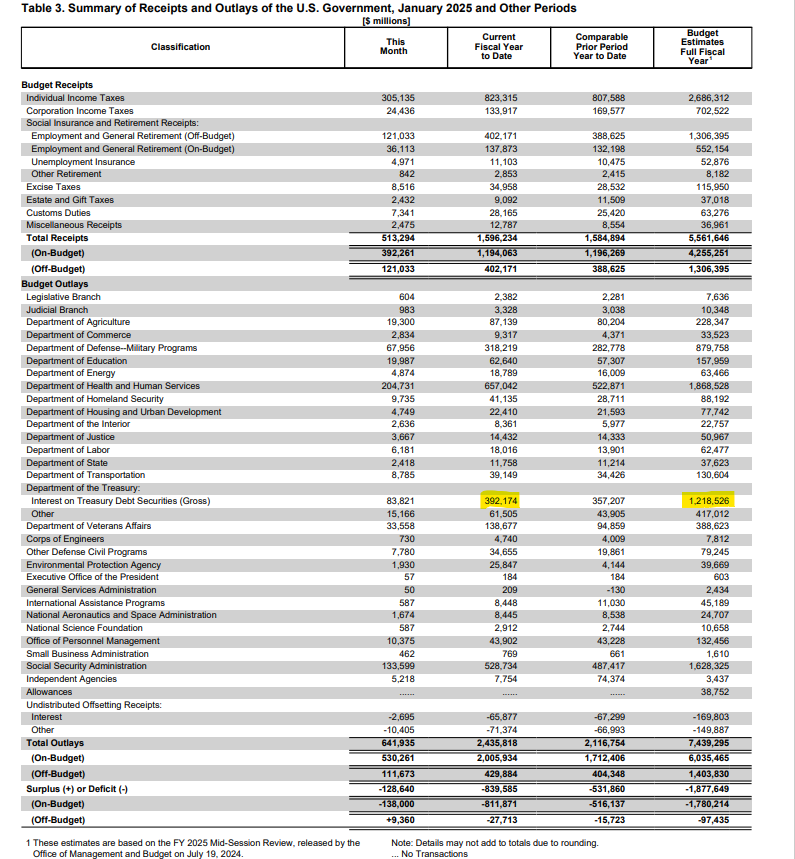
What you are looking at is a block of 10-year US Treasuries that need to be rolled over in a couple of days. Particularly, $66B 10Ys that were issued in February 2015 when interest rates were 2.00%. They'll be rolling over in a few days at 4.55%, representing an additional $1.67B in interest expense on the debt per year. While that may not seem a lot in a world where governments and central banks throw trillions around like their going out of style, it is important to realize that this is just one block of bonds that needs to be rolled over this year. If my memory serves me correctly, the Treasury needs to roll over ~$6 TRILLION in debt in the first half of this year. Using some back of the napkin Marty math skills, if all that debt rolled over at the same interest rate, that would add another ~$150B to the annual expense we pay on the interest on that debt. And in case you missed it, earlier this week the United States surpassed an incredible milestone; we are now paying $100B a MONTH in interest expense on the debt and $1.2T per year.
If all of the debt that needs to be rolled over in the first half of the year is rolled over where interest rates stand today, it will increase the annual debt expense by more than 10%. Not great, Bob!
The actions of DOGE are incredible to see, but you simply can't eliminate debt that has already been accrued by raiding the Treasury and ousting corrupt bureaucrats. The United States has an obligation to pay back those who hold our debt and the only way to do that is to produce a surplus that allows the government to pay down what has been accrued or issue new debt at wherever rates find themselves at the time of roll over to pay it back. While spending cuts are being made we, unfortunately do not find ourselves reaping the benefits of a government surplus at the moment, so we'll have to roll over the debt.
With interest rates where they are, the increase on the debt expense may put the United States government in a position where it becomes impossible to take care of the debt issue without printing their way out of it or getting all of the world's leaders around the table for a Bretton Woods-like monetary reset. We'll see how it plays out.
One thing I know for damn sure is that no matter how the US decides to deal with the debt issue, bitcoin is going to benefit massively. If they print their way out people are going to flee to scarce assets, and bitcoin is the scarcest asset on the planet outside of time. If they reset the monetary order people are going to flee to bitcoin due to the certainty of its monetary policy and its relative inability to be corrupted.
Now for...
## An Incredibly Simple Yet Powerful Quote
As discussed in my recent conversation with Porter Stansberry, the mounting U.S. government debt problem has created an intriguing dynamic for Bitcoin holders. Porter articulated a compelling perspective: government debt, which threatens most people's savings and financial security, actually becomes an asset for Bitcoin owners. The logic is straightforward – as debt levels become unsustainable, more people will be forced to flee the traditional financial system, driving demand for alternative stores of value like Bitcoin.
*"Their debt is your problem until you own Bitcoin. And then the moment you own bitcoin their debt is your greatest asset."* - Porter Stansberry
This thesis becomes even more relevant when considering the staggering numbers we discussed. The U.S. currently faces $37 trillion in on-balance-sheet debt, plus an additional $190 trillion in unfunded liabilities from Medicare, Medicaid, and Social Security. These obligations, as Porter and I agreed, are mathematically impossible to fulfill without significant monetary debasement. This reality creates a powerful tailwind for Bitcoin adoption, as it positions the asset as one of the few viable escape hatches from a system drowning in debt.
[Check out the full podcast](https://www.youtube.com/watch?v=2f8LWO_RmtU&ab_channel=TFTC) here for more on Trump's economic strategy, the commercial real estate crisis, and the future of energy markets in America.
## Headlines of the Day
Bitcoin's Realized Cap Reaches Record High - via [X](https://x.com/TFTC21/status/1889831485701833056)
Texas Bill Removes $500M Cap on State Bitcoin Purchases - via [X](https://x.com/BitcoinPierre/status/1889821134021075012)
ETF Demand Outpaces Mining Production - via [X](https://x.com/TFTC21/status/1889779939982840185)
U.S. Interest Expense on the National Debt Hits $1.2T - via [X](https://x.com/TFTC21/status/1889764204208324764)
## Bitcoin Lesson of the Day
Bitcoin transactions work by sending entire "outputs" (batches of bitcoin) rather than spending partial amounts. When spending bitcoin, the entire output must be used and split into new outputs. For example, if you have a 25 BTC output and want to spend 1 BTC, you'd create two new outputs: 1 BTC to the recipient and 24 BTC back to yourself as change. The original 25 BTC output becomes spent and unusable.
When making a payment that exceeds any single output you own, multiple outputs can be combined as inputs in a transaction. For instance, to spend 4.2 BTC, you might combine outputs of 1 + 0.5 + 2 + 1 BTC as inputs, creating new outputs of 4.2 BTC (payment) and 0.3 BTC (change).
Transaction fees are created by making the total output amount slightly less than the input amount. The difference becomes the fee, which miners collect when including the transaction in a block. The balance of a bitcoin address is the sum of all its unspent transaction outputs (UTXOs).
[Outputs | What is a Transaction Output?
A simple explanation of transaction outputs and how they work.](https://learnmeabitcoin.com/beginners/guide/outputs/)
ICYMI Fold opened the waiting list for the new Bitcoin Rewards Credit Card. Fold cardholders will get unlimited 2% cash back in sats.
[Get on the waiting list](https://foldapp.com/credit-card?r=BgwRS) now before it fills up!
$200k worth of prizes are up for grabs.
Ten31, the largest bitcoin-focused investor, has deployed $150M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at [ten31.vc/funds](ten31.vc/funds).
-

@ e3ba5e1a:5e433365
2025-02-13 06:16:49
My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get [this line](https://www.youtube.com/shorts/kqsomjpz7ok):
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song [Devil Went Down to Georgia](https://youtu.be/ut8UqFlWdDc) that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” *is*, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people *should* be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is *freedom*. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are *definitionally* better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In *Devil Went Down to Georgia*, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
*Libertas magnitudo est*
-

@ e373ca41:b82abcc5
2025-02-13 22:27:58
*This article has been written with the* ***[Pareto client](https://pareto.space/read).*** *(read it there for the full experience). It was first published in German by Milosz Matuschek on* ***["Freischwebende Intelligenz".](https://www.freischwebende-intelligenz.org/p/unterwanderter-journalismus-der-mediale)***
***
It is unmistakable. The hydra of the Deep State is losing a few heads - and this time it's the turn of the media heads. Anyone can look at [USASpending](https://www.usaspending.gov/) to see how much taxpayers' money has gone to whom in the USA.
### When the state pays its advocates
The mainstream media were also among the beneficiaries: Politico (100% Axel Springer) received over [USD 7 million](https://www.usaspending.gov/recipient/fa0cefae-7cfb-881d-29c3-1bd39cc6a49e-C/latest); the New York Times received over USD 40 million. Thousands of (probably not always necessary) government subscriptions flowed to large media houses - paid for with taxpayers' money. A form of covert press financing by the state. At what point can or should we speak of state media?
")
However, this is only the tip of the iceberg. The CIA front organization USAID ([known for its funding of virus research in Wuhan and other questionable activities](https://pareto.space/a/naddr1qqxnzden8quryveexq6rywp3qgswxu72gyq7ykjdfl9j556887jpzwu3mw3v9ez36quas55whq4te3grqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsz9nhwden5te0wfjkccte9ehx7um5wghxyctwvszsxfjh)) - [pumped USD 472.6 million directly into the media landscape via the “Internews Network”.](https://www.zerohedge.com/political/usaid-funded-massive-global-state-propaganda-news-matrix-nearly-billion-people-reach) FAZ journalist Udo Ulfkotte once called this “bought journalists” in a very clear and media-effective way, which was not good for his health. There is ample evidence of the CIA-USAID connections, for example [here](https://timesofindia.indiatimes.com/toi-plus/international/how-usaid-worked-alongside-cia-in-vietnam-a-whistleblowers-account/articleshow/118164225.cms), [here](https://foreignpolicy.com/2014/04/03/cuban-twitter-and-other-times-usaid-pretended-to-be-an-intelligence-agency/) and [here.](https://www.jstor.org/stable/4017728)
")
But this is now over for the time being: USD 268 million, which was to go to “independent media for the free flow of information” (according to the [Columbia Journalism Review](https://www.cjr.org/the_media_today/usaid-and-the-media-in-a-time-of-monsters.php)) in 2025, has been frozen. The largest media influence machine in the Western world is bleeding a little. One has to admit: part of the media-deepstate swamp is actually being drained dry financially. The fact that the Columbia Journalism Review doesn't even seem to notice that “free international journalism”, which, as it writes, is largely funded by USAID, ceases to be “free journalism” speaks volumes about this “hotbed of journalism”. Matt Taibbi of Racket News rightly finds, “The legacy media system is dead. They just don't know it yet.”
***
ADVERTISEMENT:
*Looking for the easiest way to buy Bitcoin and store it yourself? The **[Relai app](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. **[Here you can buy Bitcoin](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.*
*Need more security? The **[Trezor wallets](https://trezor.io/trezor-safe-5-bitcoin-only?transaction_id=102e192a206d1585e56a2fddef6d83\&offer_id=238\&affiliate_id=35234)** are recommended and easy to use, others are available in the **[store](https://trezor.io/?transaction_id=102bc85bdca2733287749c7f879ebd\&offer_id=133\&affiliate_id=35234)**. Need more advice? Book an **[introductory meeting](https://trezor.io/trezor-expert-session?transaction_id=1020e18dad0aa4b1186289fd22e90f\&offer_id=241\&affiliate_id=35234)** with a wallet expert.*
***
Large-scale media manipulation has become visible. The propaganda matrix, if you will. The disastrous thing about it: if the Overton window is infiltrated, so to speak, the entire institution of journalism cannot be trusted. Every day, readers must expect to be pulled through the nose ring of intelligence service narratives and public agendas by mainstream journalists who pretend to be objective (and are often simply clueless and unsuspecting). The panorama of what we are supposed to see and believe, so to speak.
How many mainstream journalists today are basically mouthpieces for the services? Every mainstream reader must now ask themselves: Is my favorite journalist at NZZ, Welt, SZ, ZEIT or FAZ perhaps just a CIA-IM? There were no major dissenters among them: EU criticism? Vaccination criticism? Criticism of NATO? Criticism of Biden and America? Criticism of Nord Stream? There were brief moments on television when questions about journalists' ties to lobby organizations were still part of the German satire program.
<https://x.com/Spitze_Zunge_/status/1887915509988876786>
### The cards in the media are being reshuffled
The watchdog of the powerful has been infiltrated by the powerful. This means that the Fourth Power is not a power at all, but part of the executive branch, a mouthpiece of the government. The claim that the mainstream is quality journalism, the gold standard for trustworthy information, is therefore the real fake news. It is the last, now crumbling dogma of an infiltrated press sect that has formed a cartel and is subjecting citizens to a permanent psy-op with intelligence-controlled taxpayers' money. A troupe of spokespeople at the work of mental synchronization.
<https://x.com/TopherField/status/1887962959072149989>
### The fight against independent media
But they not only give to one, they also take from the other. While government agencies use taxpayers' money to promote a certain type of journalism, the juice is actively being cut off from the critical part. All it takes is to be classified as a “PEP” (politically exposed person) and the bank account is gone. This is what has just happened to swiss Radio Kontrafunk. The critical Swiss author Stefan Millius was canceled by his publisher. Others have had their monetization via YouTube cut off (Snicklink). Others are harassed by the state media authority (Multipolar, Alexander Wallasch). The next one has a house search. It has been known since the Twitter files that the government and services also intervened massively in social media communication. This is no longer the Cold War. But it is the cold information war.
<https://www.youtube.com/watch?v=kmgWAGDFCZI>
Is this all so outrageous and new? During the Cold War, the CIA systematically infiltrated media outlets in the US. Thousands of agents were deployed as journalists - and wrote what they were told. This “Operation Mockingbird”, which the Church Committee also investigated, never ended, so to speak. It lives on as Operation Mockingbird 2.0.
Intelligence payments to media outlets continue to exist.
USAID distributes millions for “pro-democratic” reporting.
Government subscriptions keep uncritical media alive.
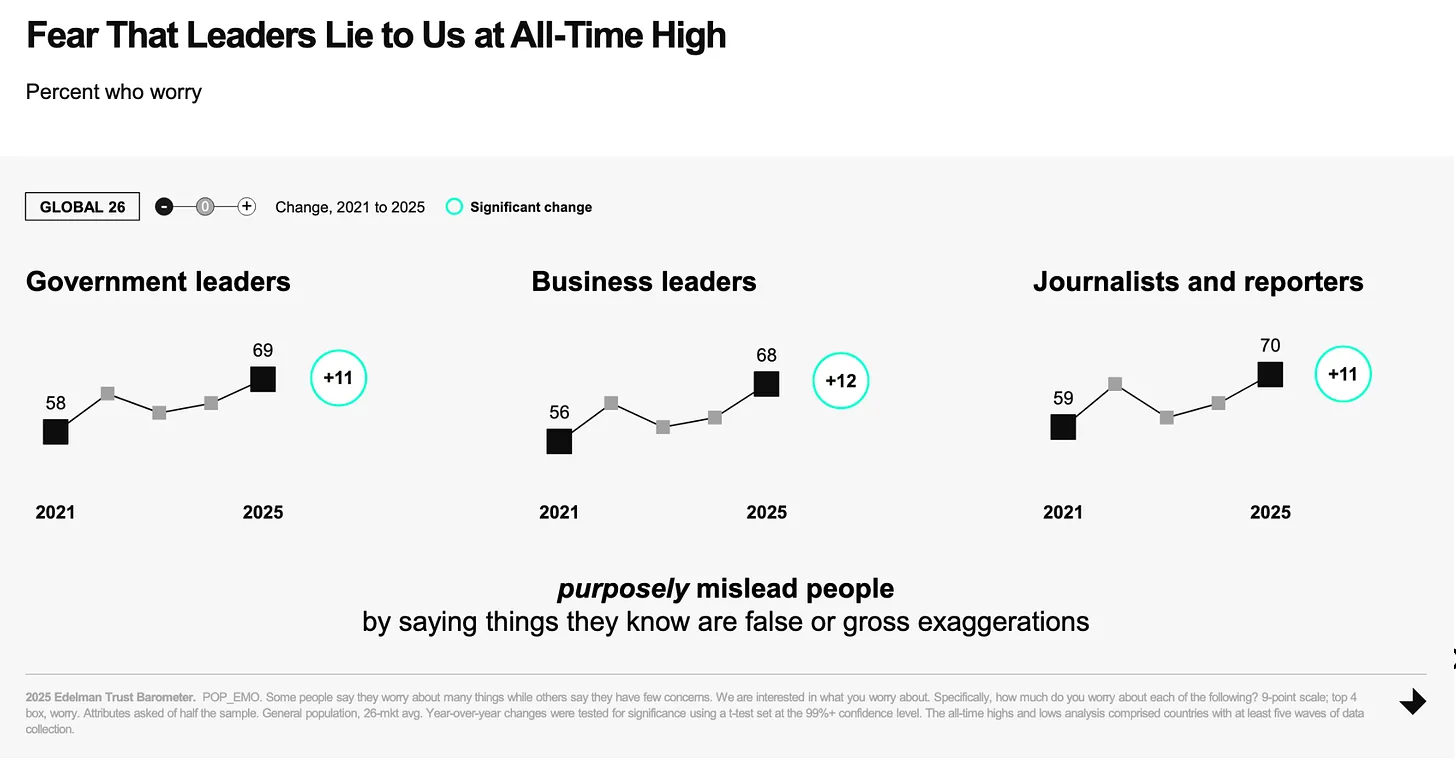
Media control of public opinion is the most important tool of power in a modern “democracy”. The difference to back then? Today, the manipulation is global. However, these revelations come at a time when trust in the media is already at an all-time low. [The fear of being lied to by the powerful is currently the majority opinion at 70%.](https://www.edelman.com/trust/2025/trust-barometer) They are currently in the process of convincing the remaining 30% of their own incompetence.
### Update on the [Pareto project](https://pareto.space/en)
“Half the victory”, says Sun Tsu, ‘lies in the impregnable defense’. Free media now have the opportunity to build their own impregnable bastion and the [Pareto Project](https://pareto.space/read) invites them to do just that: [become uncensorable, be able to scale infinitely and not depend on third parties for all processes of journalistic work](https://pareto.space/a/naddr1qqxnzdenxuerxdpkxycngvpcqgsvlutjpemmkp50p6aa8zwu65yz9hg6erf2czc0tuyqpt57zhr79vsrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hs33ee7d). It's all possible now. Everyone has to realize that: With other platforms, you build your house on someone else's property. With Nostr/Pareto, there is nothing and no one between author and reader, both in terms of communication and payment (via Bitcoin/Lightning).
**A brief update on the project, January was very busy.**
* We have about 35 journalists, publications, substackers, bloggers, memers onboarded who publish texts via the Pareto client, and the number is growing all the time.
* The first Telepolis authors, such as Mathias Bröckers and Alexander Unzicker, will soon be able to re-publish their deleted texts with us in a censorship-proof manner, and we are helping with the migration of content.
* We recently successfully tested the newsletter function! We will soon be able to offer all authors and readers the functions of Substack, Steady, Ghost etc. without having to entrust their readers' sensitive data to a platform or expose them to platform tracking.
* We are delighted to have more high-caliber additions to our development team, which now comprises around ten wonderful people, almost all of whom come from this group of readers.
* Our [open source code is now also public.](https://github.com/twenty-eighty/pareto-client)
* We have opened a [crowdfunding on Geyser!](https://geyser.fund/project/pareto)
- Our editor will soon be available to everyone free of charge (atm you have to drop us your npub: <team@pareto.space>)
### What's next?
This opens up a new window of unimagined possibilities: On a strong basis such as that offered by decentralized technology, many critical authors can now publish securely or new publications can be created - worldwide and uncensorable. What kind of publications would you like to see? Where do you see gaps (also in the critical spectrum) that need to be filled, both in terms of formats and topics? What does the journalism of the future look like to you? Feel free to write to me: **<milosz@pareto.space>**
## One last thing
Our funds are coming to an end. If you would like to support us: We have started a [crowdfunding on Geyser](https://geyser.fund/project/pareto), where you can help us with Bitcoin/Lightning donations. 
For traditional donations, you can find our bank account on our **[landingpage.](https://pareto.space/en)**
***
***Join the marketplace of ideas!** We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the [Pareto Project](https://pareto.space/en)? Zap me, if you want to contribute (all Zaps go to the project).*
*Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to **<team@pareto.space>***
**Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)**
-

@ dbb19ae0:c3f22d5a
2025-02-13 20:42:08
Installation:
``` bash
python3 -venv nostr-sdk
source nostr-sdk/bin/activate
pip install nostr_sdk requests
```
Python program:
``` python
# Usage example: python ns_read_metadata.py nostr:npub1mwce4c8qa2zn9zw9f372syrc9dsnqmyy3jkcmpqkzaze0slj94dqu6nmwy
# Compatible with version 0.39
# ns_read_metadata.py
# version 3
import asyncio, argparse, json
from nostr_sdk import Metadata, Client, NostrSigner, Keys, Filter, PublicKey, Kind
from datetime import timedelta
async def main(npub):
client = Client()
await client.add_relay("wss://relay.damus.io")
await client.connect()
pk = PublicKey.parse(npub)
print(f"\nGetting profile metadata for {npub}:")
metadata = await client.fetch_metadata(pk, timedelta(seconds=15))
print(metadata)
if __name__ == '__main__':
parser = argparse.ArgumentParser(description='Fetch all metadata for a given npub')
parser.add_argument('npub', type=str, help='The npub of the user')
args = parser.parse_args()
asyncio.run(main(args.npub))
```
-

@ dd664d5e:5633d319
2025-02-12 07:05:51
I think this note from Chip (nostr:npub1qdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havq03fqm7) is one of those things that people with business management experience take a lot more seriously than most developers and influencers do.
I am painfully aware of the cost of systems administration, financial transaction management and recordkeeping, recruiting and personnel management, legal and compliance, requirements management, technical support, renting and managing physical spaces and infrastructure, negotiating with suppliers, customer service, etc. etc.
There's this idea, on Nostr, that sort of trickled in along with Bitcoin Twitter, that we would all just be isolated subsistance farmers and one-man-show podcasters with a gigantic server rack in the basement. But some of us are running real companies -- on and off Nostr, for-profit and non-profit -- and it often requires a lot of human labor.
The things we build aren't meant to be used by one person and his girlfriend and his dog. Yes, he can also run all these things, himself, but he no longer has to. Our existence gives him the choice: run these things or pay us to run them and spend your time doing something else, that you do better than we do.
These things are meant to be used by hundreds... thousands... eventually millions of people. The workflows, processes, infrastructure, and personnel need to be able to scale up-and-down, scale in-and-out, work smoothly with 5 people or 50 people. These are the sort of Nostr systems that wouldn't collapse when encountering a sudden influx or mass-escape. But these systems are much more complex and they take time to build and staff to run them. (And, no, AI can't replace them all. AI means that they now also have to integrate a bunch of AI into the system and maintain that, too.)
GitCitadel (nostr:npub1s3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqd975wz) is very automation-forward, but we still have to front the incredibly high cost of designing and building the automation, train people to interact with it (there are now over 20 people integrated into the workflow!), adjust it based upon their feedback, and we have to support the automation, once it's running.
This sort of streamlined machine is what people pay companies for, not code. That is why there's little business cost to open source.
Open-source is great, but...
nostr:nevent1qqsgqh2dedhagyd9k8yfk2lagswjl7y627k9fpnq4l436ccmlys0s3qprdmhxue69uhhg6r9vehhyetnwshxummnw3erztnrdakj7q3qqdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havqxpqqqqqqzdhnyjm
-

@ 3ad01248:962d8a07
2025-02-13 20:03:40
I feel like this is go to be a common phrase over the next four years. While I generally like most of the policies that he is in favor of, I for the life of me can't understand his position on Gaza. It sounds like nothing like the Trump for the campaign trail whatsoever.
When he ran for president last year he ran on a platform of not starting any new wars. Having a US solider set foot in Gaza is a recipe for disaster and chaos. Sending in the military is not "America First". Gaza has no national security implication for the United States so obviously there is a different reason why President Trump is proposing this idea.
We have to look at who funded his campaign to understand his motives by wanting to clear out Gaza and rebuild it like it some real estate deal.
## Miriam Adelson
[Miriam Adelson the wife of late casino magnate Sheldon Adelson](https://www.timesofisrael.com/miriam-adelson-gives-100-million-to-trump-campaign-making-good-on-reported-pledge/) gave Trump $100 million to help get Trump elected. Mrs. Adelson is a pro-Israel and supports a variety of Jewish causes. $100 million buys you a lot of political favors if you ask me. Mrs. Adelson and her husband were the power behind the scene of the first Trump administration to get them to move the US embassy to Jerusalem.
She also own the largest newspaper in Israel which means she has the ability to impact public opinion inside the country. As you can see this is person with a tremendous amount money and social capital to spend and she is undoubtedly using it to get Trump to purge Gaza of the native Palestinians.
Who else is in Trump's ear that influence him to come up with crazy idea?
### Jared Kushner
We all know that Trump values family and loyalty above all else so it is no surprise that Trump would listen to someone in his family for guidance on what to do in Gaza. Jared Kushner is that guy for Trump. As the son-in-law of is favorite daughter you can bet that he is going to listen to what he has to say. Funny you listen to Trump and I swear that you hear Jared come out of his mouth.
Back in March 2024 Kushner suggest the very idea that Trump is talking about right now! Almost verbatim to be honest. Here is a link to a talk where Kushner laid out what he thought should happen to Gaza and the Palestinians.
https://www.youtube.com/watch?v=nneWrllngAU
When you listen to it, you see that Trump basically took this idea from Kushner and made it his own.
Who is exactly is running the show in the White House? Trump seems to be doing the bidding of everyone else except the American people. Who else is Trump listening to on the Gaza issue?
#### Bibi Netanyahu/Israeli Far-Right
Last but not least is the persons behind all the death and mayhem in Gaza. Trump absolutely sides with the Israeli narrative spun by Bibi Netanyahu and the Israeli far right characters such as Itamar Ben-Gvir and Bezalel Smotrich. This trio have a distinct hatred of Palestinians and do not want to see the creation of a Palestinian state.
They want to see occupied West Bank annexed by Israel and all of the Palestinians there to leave or be subjugated to Israeli rule.
Just take a look at the worldview of these people and they have power within the halls of the Israeli government.
https://www.jpost.com/Israel-News/Politics-And-Diplomacy/Bayit-Yehudi-MK-causes-uproar-by-saying-God-commanded-Jews-not-to-sell-homes-to-Arabs-409241
https://hashiloach.org.il/israels-decisive-plan/
https://www.reuters.com/article/idUSKBN0MC1I7/
When you have this world view how is peace even possible? It's not because they don't want peace and quite frankly I don't know if its possible at this point. Israelis and Palestinians have diametrically opposing views of what the land should be.
Israeli believe that the land should be exclusively governed by Jewish people whereas the Palestinian view from what I understand just want to return to the lands they were kicked out from and deal with governance later.
There are elements on both side that want this conflict to go on forever because it gives the outsized power, namely Hamas on the Palestinian side and the Israeli Far Right on the Jewish side. I would guess that a majority of people in the middle would have no problem living side by side with each other as long as rights and freedoms were respected.
A one state solution looks like the most reasonable solution to me but the odds of that happening are slim to none right now.
President Trump has the power to change the middle east for the better if he had the backbone do to what is right but it looks like he is going to listen to people the want war, genocide and ethnic cleansing.
-

@ c69b71dc:426ba763
2025-02-11 14:07:34
# The Power of Words...
## ...Shaping a Compassionate Future
This morning I woke up with this thought:
**> If we were more mindful of our choice of words, we would immediately need to change the following: Schools would no longer have classes and classifications, but only Communities!**
This would make a huge difference in terms of togetherness, well-being, and caring for one another. 🙌🏼
### Language shapes reality
Words influence how we see the world and ourselves. When we replace terms like "classes" or "grades" with "community" and "development," it changes our entire way of thinking about education and coexistence.
For example, in companies, we often talk about "teams" instead of "departments." This unconsciously fosters unity, cooperation, and a sense of belonging on equal terms.
### Community instead of competition
In school, work, and everyday life, we often evaluate, compare, and classify. But what if we focused on cooperation and synergies instead of competition?
In some schools, there are no grades anymore, just individual feedback – this takes away the performance pressure and strengthens intrinsic motivation.
### Appreciation instead of categorization
Putting people in "boxes" – whether through grading systems, social classes, or job titles – often creates separation rather than connection.
Instead of labeling people as "successful" or "failed," we could ask: "What are their strengths? How can we support each other?"
Mindful language in everyday life
We could also reflect on our word choices in daily life:
Instead of "problem" → "challenge"
Instead of "failure" → "learning opportunity"
Instead of "mistake" → "experience"
### School as a mirror of society
How we learn to interact with each other in school shapes our behavior in society. When children grow up in communities instead of class systems, they learn that cooperation and empathy are more important than competition.
There are so-called democratic schools where there are no grade levels – children learn from each other across ages. Students support each other by sharing knowledge and helping each other. Teachers are seen as coaches, not as "all-knowing" authority figures.
They too are human and can learn from the children.
Many teachers want to give children something that will help them in life.
However, the rigid old school system dictates what must be taught and when, often disregarding the individual interests of the children. This stifles passions – in both the children and the teachers. Instead, teachers could act as inspiring sparks, igniting curiosity and enthusiasm for learning.
-----------
> **A history teacher once said to me on the phone, when discussing my son who didn’t want to read printed Wikipedia sheets: "If there is no spark in the child, the teacher can’t ignite anything."
**
This sentence frustrated me, because it shows that this teacher had long since lost his own spark!
**Children always have a spark. Always!**
-----------
### A day without evaluations
What if we consciously refrained from evaluating others for one day – whether through grades, criticism, or labels?
Instead of saying to a friend, "You made a mistake," we could say, "That was an interesting experience – what did you learn from it?"
Instead of saying, "That wasn’t good," we could ask, "How could it be done differently or better?"
Instead of grading children in school, we could tell them what they did well and where they can still grow.
Instead of getting upset about a difficult customer, we could feel empathy for their situation.
### Mindful language as the key to change
**If we are more mindful with our language – also with how we speak to ourselves – we can shape a society where people meet each other with compassion. **
`Words are vibrations that shape reality. Chosen consciously, they can create a world based on connection, growth, and love.
It is up to us to start this change within ourselves – and carry it into the world.`
Thank you for reading 🕊️

-

@ 21ffd29c:518a8ff5
2025-02-13 20:03:17
**Introduction:**
Self sovereignty is a pivotal concept in understanding personal autonomy across various ideologies, including, libertarianism, socialism and individualism. This article explores how the statement "I own myself" by the Ole Voyager in the 1600's encapsulates this principle, emphasizing empowerment and self-management.
**Article:**
- **What is Self Sovereignty?**
- **Definition:** It refers to the ability of an individual or group to govern themselves without external imposition.
- **Core Principles:**
- Autonomy: The right to manage one's own affairs independently.
- Equality: Recognition of equal rights and responsibilities among individuals.
- **Historical Context:** Rooted in ideas from liberalism, socialism, and feminism, advocating for personal freedom and equality.
- **The Significance of 'I Own Myself'**
- **Statement Explanation:** The Ole Voyager's quote highlights personal ownership over one's life, values, and destiny.
- **Contrast with Traditional Views:** Shifts from societal control to individual responsibility, advocating for personal agency.
- **Implications:** Encourages owning health, relationships, knowledge, and cultural identity, promoting a holistic view of self-worth.
**Conclusion:**
Understanding self sovereignty through the Ole Voyager's statement is crucial. It empowers individuals by asserting their right to manage their lives autonomously. This concept not only enhances personal freedom but also challenges societal structures, fostering inclusive governance that respects individual rights and equality.
Not everyone has the capacity to be a sovereign and self govern themselves. Some are quite content to be told what to do and how to do it. Others are very happy to be on the dole and get free things in exchange for trinkets.
This empowerment can lead to more equitable societies where individuals thrive within their own means, emphasizing empowerment and collective responsibility.
-

@ 30b99916:3cc6e3fe
2025-02-13 18:56:37
## Upgrade Details
Download current release and manifest files
```shell
Navigate to https://github.com/getAlby/hub/releases/tag/v1.13.0/
Download
albyhub-Server-Linux-x86_64.tar.bz2
manifest.txt
manifext.txt.asc
Copy the downloaded files to $HOME
mv $HOME/Downloads/albyhub-Server-Linux-x86_64.tar.bz2 $HOME
mv $HOME/Downloads/manifest.txt $HOME
mv $HOME/Downloads/manifest.txt.asc $HOME
```
Verify manifest signature & Checksum
```sh
Only need to import once
curl https://raw.githubusercontent.com/getalby/hub/master/scripts/keys/rolznz.asc | gpg --import
gpg --verify manifest.txt.asc manifest.txt
gpg: Signature made Tue 07 Jan 2025 08:56:42 PM PST
gpg: using RSA key 5D92185938E6DBF893DCCC5BA5EABD8835092B08
gpg: Good signature from "Roland Bewick <roland.bewick@gmail.com>" [unknown]
gpg: WARNING: This key is not certified with a trusted signature!
gpg: There is no indication that the signature belongs to the owner.
Primary key fingerprint: 5D92 1859 38E6 DBF8 93DC CC5B A5EA BD88 3509 2B08
shasum -a 256 server-linux-x86_64.tar.bz2
a75c03d241921611dfc428c413c4a2c2cef35bc6d1974839b688ef462604058d server-linux-x86_64.tar.bz2
The above checksum should be referenced in the manifest.txt file
cat manifest.txt
```
Stop AlbyHub & Backup existing data directory & Binaries
```shell
systemctl stop albyhub
cp -r $HOME/.local/share/albyhub /media/veracrypt1/albyhub
cp $HOME/bin/albyhub $HOME/bin/albyhub172
cp -r $HOME/lib $HOME/lib172
```
Extract new release Binaries & Start AlbyHub
```sh
tar -xvjf albyhub-Server-Linux-x86_64.tar.bz2
./
./lib/
./lib/libglalby_bindings.so
./lib/libldk_node.so
./lib/libbreez_sdk_bindings.so
./bin/
./bin/albyhub
systemctl start albyhub
```
Navigate to http://localhost:9090
-

@ dbb19ae0:c3f22d5a
2025-02-13 17:46:41
This code below works with nostr_sdk 0.32.2
``` python
import asyncio, argparse, json
from nostr_sdk import Metadata, Client, NostrSigner, Keys, Filter, PublicKey, Kind
from datetime import timedelta
async def main(npub):
client = Client()
await client.add_relay("wss://relay.damus.io")
await client.connect()
pk = PublicKey.from_bech32(npub)
print(f"Getting profile metadata for {npub}:")
f = Filter().kind(Kind(0)).author(pk).limit(1)
events = await client.get_events_of([f], timedelta(seconds=15))
if events:
event = events[0]
metadata_dict = json.loads(event.content())
for key, value in metadata_dict.items():
print(f"{key}: {value}")
else:
print("Could not retrieve metadata for the given public key.")
if __name__ == '__main__':
parser = argparse.ArgumentParser(description='Fetch all metadata for a given npub')
parser.add_argument('npub', type=str, help='The npub of the user')
args = parser.parse_args()
asyncio.run(main(args.npub))
```
but with nostr_sdk 0.39
the program no longer worked and crash with error:
```
AttributeError: type object 'PublicKey' has no attribute
'from_bech32'. Did you mean: 'to_bech32'?
```
why?
---
source:
- https://github.com/ev3rst/nostr_sdk_examples
- https://alashazam.wordpress.com/2024/07/07/python-nostr_sdk-fetching-all-metadata/
-

@ 89ccea93:df4e00b7
2025-02-13 17:34:06
**[Original Post](https://expatriotic.me/grapheneos/)**
## Core Philosophy
1. **Privacy ≠ Optional**: Prevents mass data collection by design
2. **Security > Convenience**: Sacrifices "smart" features for exploit resistance
3. **Transparency**: Every line of code [auditable](https://github.com/GrapheneOS)
4. **Device Sanity**: Removes 2M+ lines of Google telemetry code
5. **Proactive Hardening**: Replaces reactive "vulnerability whack-a-mole" with systemic memory safety improvements. 73% of Android CVEs prevented via Scudo++ allocator and Rust integration.
6. **Hardware Paradox**: Uses Google Pixels *because* of their Titan M2 secure enclave (physically separate from main CPU, Verified Boot with user-defined root of trust, Firmware-level MAC randomization (prevents Wi-Fi tracking)).
7. **Support Superiority**: GrapheneOS support for Pixel phones is 2 years longer Google's.
> *"We're eliminating entire vulnerability classes - not just patching holes."*
## **History**
* Born in **2014** as **CopperheadOS**
* **2016**: First Pixel support (Google's hardware + de-Googled OS)
* Rebranded in **2019** after a developer split. Focuses exclusively on Pixel phones.
* **2021**: **Scudo++** with quarantines (NSA-grade exploit mitigation)
* **2023**: Full Rust integration (prevents buffer overflows in core OS)
* **2023**: Controversial lead dev, Daniel Micay, stepped down but remains director
* **2024**: Quantum-resistant encryption prototypes
> *"Our Auditor app detects hardware tampering better than Apple's T2 chip."*
## **Installation**
* **Minimum**: Pixel 4a
* **Recommended**: Pixel 7a (5-year update guarantee)
* **Backup data first**: unlocking bootloader wipes device
### **Beginners: Web Installer**
1. Enable OEM Unlock:
`Settings → About → Tap Build Number 7x → Developer Options → OEM Unlocking`
2. Visit [grapheneos.org/install](https://grapheneos.org/install)
3. Connect phone → Follow prompts (20 minutes)
### **Advanced: CLI install**
* Full CLI guide: [grapheneos.org/install/cli](https://grapheneos.org/install/cli) (8 minutes)
>*"We're proving iPhones aren't the only secure option - just better marketed."*
### **Post-Install Checklist**
[ ] Deny all "convenience" permissions
[ ] Enable Sensors Off toggle
[ ] Install Auditor app
[ ] Sensors Killswitch: `Quick Settings → Toggle Off`
[ ] Network Restrictions:
```markdown
Settings → Network & Internet → Firewall
- Enable per-connection MAC randomization
- Block local network discovery
```
[ ] Auditor Validation: Daily automated checks against Google's hardware certs
## Setting up
### **Priority Sources**
1. **Accrescent** (Pre-installed)
- Molly (Signal fork)
- Aves Gallery (EXIF stripping)
- AppVerifier (APK validation)
2. **Obtainium** ([GitHub](https://github.com/ImranR98/Obtainium))
```markdown
1. Search "[App] GitHub releases"
2. Copy releases page URL
3. Paste into Obtainium → Auto-updates enabled
```
- *Example*: NewPipe → `https://github.com/TeamNewPipe/NewPipe/releases`
3. **Google Play** (Last Resort)
- Use separate profile
- Burner account: Fake name + **NO phone number**
## FOSS Apps
* Accrescent - Privacy-focused app store
* Aegis - 2FA authenticator
* Amethyst - Nostr decentralized social client
* AndBible - Offline Bible study
* Antennapod - Podcast manager
* AppVerifier - APK signature validation
* Ashigaru - Bitcoin wallet with Ricochet
* Aves Gallery - Gallery with EXIF stripping
* Brave - Anti-fingerprinting browser
* Easy Noise - Offline white noise generator
* Easy Note - Minimalist notes
* Envoy - Bitcoin wallet
* IronFox - Hardened Firefox fork
* KeePassDX - Offline password manager
* Léon - URL tracking stripper
* LocalSend - AirDrop alternative
* Material Files - File manager
* Molly - Signal fork with local encyption
* Monero.com - Official Monero wallet
* NetGuard - No-root firewall
* NewPipe - YouTube client with SponsorBlock
* Nextcloud - Self-hosted cloud suite
* OpenKeychain - PGP encryption
* Organic Maps - Offline navigation
* Orbot - Tor proxy
* Proton Drive - E2E encrypted storage
* Proton Mail - Zero-access email
* RedReader - Privacy-first Reddit client
* Simple Calendar Pro - Telemetry-free calendar
* Telegram FOSS - Decentralized messaging
* Tor Browser - Onion-routed browsing
* Twidere - Twitter/Fediverse client
* Tuta - Encrypted email
* Tuta Calendar - Encrypted calendar
* Vanadium - Hardened Chromium
* Zeus - Bitcoin Lightning node
> _"Your phone is a corporate surveillance device that happens to make calls. GrapheneOS removes the spyware OS while keeping the secure hardware."_
## **Silent.Link eSIM: Anonymous Connectivity**
**No Phone Number Required**
Visit [Silent.Link](https://silent.link) → Select data plus eSIM plan (with NO phone number).
```I've used this successfully in many countries. It even gives me unfettered and free internet in China. Be sure to pick the telecom company based on what they charge per GB of data. The difference can be 100x!```
## Support the Project:
- **Donate**: [grapheneos.org/donate](https://grapheneos.org/donate)
- **Community**: [grapheneos.org/contact](https://grapheneos.org/contact)
>*"GrapheneOS isn't about becoming a privacy expert overnight. It's about systematically removing corporate surveillance hooks - one app, one permission, one profile at a time."*
## Moar Halp
* **[Side Of Burritos](https://www.youtube.com/playlist?list=PLHvdaysg3bMyYwJAcxbFUY9YqKKC0Dtrd)**
* **[Hated One interview with GrapheneOS dev Gabe](https://www.youtube.com/watch?v=WkQ_OCzuLNg)**
originally posted at https://stacker.news/items/884965
-

@ dbb19ae0:c3f22d5a
2025-02-13 17:32:36
pip cache will show how much space is taken from past download
``` bash
(nostr) ever3st@Alashazam:~/Documents/dev/python/$ pip cache info
Package index page cache location: /home/ever3st/.cache/pip/http
Package index page cache size: 2437.7 MB
Number of HTTP files: 271
Wheels location: /home/ever3st/.cache/pip/wheels
Wheels size: 2.2 MB
Number of wheels: 2
```
About 2GB
if space is needed
it can be cleared
``` bash
(nostr) ever3st@Alashazam:~/Documents/dev/python/$ pip cache purge
Files removed: 273
(nostr) ever3st@Alashazam:~/Documents/dev/python/bots/nostr$ pip cache info
Package index page cache location: /home/ever3st/.cache/pip/http
Package index page cache size: 0 bytes
Number of HTTP files: 0
Wheels location: /home/ever3st/.cache/pip/wheels
Wheels size: 326 bytes
Number of wheels: 0
```
-

@ 6538925e:571e55c3
2025-02-13 16:05:42
\
**Nostr Live Streams (Beta)**
If you follow shows like Rabbit Hole Recap, THE Bitcoin Podcast or Simply Bitcoin on Nostr, you can now watch the video in Fountain and hang out in the live chat as it’s being recorded. You'll find livestreams from people who follow on Nostr at the top of the home screen.
As well and live podcasts, you will also find live music events from PhantomPowerMedia, radio stations like NoGood and Noderunners, as well as channels dedicated to gaming, art, coding and much more.
Bringing creators and fans together through live experiences enables audience participation and creates a special feeling of community, so we’re really excited to get this into your hands.
Nostr livestreams are a beta feature - i.e. we still have a lot more work to do! We will continue to make improvements to livestreams over the coming months - so we would love to hear your feedback.
\
**Storage Manager**
We’ve added a storage manager in the app’s settings so that you can view file storage size for audio downloads, video downloads, transcripts, image cache, feed cache, and temp files. You can delete all files in any of these folders to free up storage on your device so that Fountain continues to run optimally.
There are other performance and stability improvements that we are working on too. For example, in the next couple of weeks we will be rolling out an image proxy service, which should reduce mobile data usage and optimise storage.
Stay tuned for further updates and, as always, thanks for your support.
-

@ f1989a96:bcaaf2c1
2025-02-13 14:24:32
Good morning, readers!
This week, we highlight how authoritarian regimes are manipulating digital assets. The Central African Republic launched a government-backed meme coin that crashed spectacularly within a day of launch as regime insiders cashed out for profits, leaving the public with worthless tokens.
Meanwhile, the Nigerian regime introduced its first official stablecoin, cNGN. It is issued by the African Stablecoin Consortium and is backed 1:1 with the naira. Still, it operates under the direct oversight of the Nigerian Securities and Exchange Commission, allowing further surveillance of Nigerians’ financial activity alongside the struggling eNaira CBDC.
On the freedom tech front, Mullad VPN now supports Bitcoin payments via the Lightning Network, offering activists, journalists, and individuals under oppressive regimes a censorship-resistant and permissionless way to pay for their privacy. Additionally, SeedSigner, an open-source hardware wallet for Bitcoin self-custody, rolled out multilingual support, expanding accessibility to Spanish-speaking activists and human rights defenders.\
\
Finally, journalist Frank Corva explores Africa’s grassroots Bitcoin movement, where open-source tools and circular economies are empowering communities inside authoritarian regimes with financial freedom. For those who doubt Bitcoin’s real-world impact, this article is a must-read.
**Now, let’s get right to it!**
### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a)
## **GLOBAL NEWS**
#### **Central African Republic | Launches Meme Coin Experiment**
The Central African Republic (CAR) [debuted](https://www.reuters.com/world/africa/central-african-republic-debuts-meme-coin-experiment-2025-02-10/) a government-backed meme coin, $CAR, which President Faustin-Archange Touadéra [claims](https://www.reuters.com/world/africa/central-african-republic-debuts-meme-coin-experiment-2025-02-10/) will “unite people” and “support national development.” In reality, meme coins are speculative assets that often serve as vehicles for insider profit. This scheme follows CAR’s failed [Sango Coin](https://www.mariblock.com/central-african-republic-top-court-rules-sango-coin-unconstitutional/) project, which promised citizenship and land in exchange for [locked](https://www.mariblock.com/central-african-republic-top-court-rules-sango-coin-unconstitutional/) investments but sold only 7.5% of its supply. Those who did “buy in” did not receive what was promised. In 2022, CAR briefly made Bitcoin legal tender, calling it a path to sovereignty — only to [abandon](https://bitcoinmagazine.com/culture/why-bitcoin-failed-in-car) it shortly after. Instead of supporting open and neutral money like Bitcoin, the government has turned to dubious crypto schemes. The real beneficiaries of $CAR appear to be regime insiders who reportedly cashed out [$40 million](https://x.com/bored2boar/status/1889002901370196098) while the public holds [worthless](https://decrypt.co/305225/central-african-republic-president-meme-coin) tokens.
#### **Nigeria | Debuts Naira Stablecoin**
The Nigerian state [launched](https://www.mariblock.com/move-over-enaira-cngn-enters-the-chat-2/) its first regulated stablecoin, [cNGN](https://cngn.co/?ref=mariblock.com). Similar to US dollar-pegged stablecoins like USDT and USDC, cNGN is pegged 1:1 to its local currency (the naira). It is issued by the African Stablecoin Consortium (ASC), a private coalition of Nigerian financial institutions and blockchain companies. Positioned as a bridge between fiat and digital assets, cNGN aims to facilitate remittances and trade but comes with strict verification requirements that limit financial privacy. The Nigerian SEC also tightly regulates the stablecoin and it is only available on government-approved exchanges, Busha and Quidax. As Nigeria expands its control over digital transactions — through both cNGN and its struggling [eNaira CBDC](https://cbdctracker.hrf.org/currency/nigeria) — more and more Nigerians are [turning](https://www.forbes.com/sites/digital-assets/2024/01/08/central-bank-of-nigeria-approves-naira-stablecoin-for-2024-launch/) to Bitcoin as a censorship-resistant alternative.
#### **Russia | Proposes Registry to Track Bitcoin Mining Hardware**
Russia’s deputy energy minister, Yevgeny Grabchak, has [proposed](https://theminermag.com/news/2025-02-03/russia-minister-bitcoin-miner/) a centralized registry of Bitcoin mining equipment and wallet addresses to “identify mining activities and ensure stricter enforcement of bans in restricted regions,” such as Russian-occupied Ukraine territories. Meanwhile, the Chairman of the State Duma Committee on Energy, Nikolai Shulginov, warned that last year’s mining ban in several Russian and occupied regions may not be enough to eliminate mining fully. As an authoritarian state with an egregious human rights record and a long history of financial repression, Russia appears intent on tightening surveillance of economic activity — especially that of Bitcoin. By registering, tracking, and restricting mining, the Kremlin expands its financial control, undermines economic autonomy, and limits access to permissionless money.
#### **Turkey | Erdoğan Targets Opposition as Inflation Forecast Rises**
Turkish President Recep Tayyip Erdoğan sentenced Istanbul Mayor Ekrem Imamoglu — a key political rival — to [seven](https://www.bloomberg.com/news/articles/2025-02-05/turkey-s-main-rival-to-erdogan-faces-jail-time-in-new-indictment) years in prison on charges widely seen as politically motivated. If upheld, the conviction will bar Imamoglu from office, further clearing Erdoğan’s path to dominance ahead of the 2028 elections. At the same time, Turkey’s economic crisis is worsening. [Accelerating inflation](https://www.reuters.com/world/middle-east/turkey-cenbank-raises-inflation-forecast-says-not-autopilot-with-cuts-2025-02-07/) forced the central bank to raise its 2025 forecast from 21% to 24%, exacerbating the lira’s decline and eroding purchasing power. As both political and financial repression deepen, more Turks are turning to alternatives to sidestep Erdoğan’s expanding control over the economic and political sphere.
#### **Georgia | Regime to Pass Censorship Law**
Georgia’s ruling Georgian Dream party is set to introduce a media censorship [law](https://jam-news.net/georgian-dream-plans-to-pass-media-censorship-law/) aimed at enforcing government-defined standards for journalistic objectivity and ethics, while also restricting foreign funding for media outlets. MP Mamuka Mdinaradze [claims](https://jam-news.net/ngos-and-media-organizations-of-georgia-to-challenge-the-foreign-agents-law-in-strasbourg-court/) the law will establish monitoring mechanisms and is modeled after UK regulations, though critics [compare](https://jam-news.net/opinion-ivanishvili-adopts-belarusian-tactics-to-control-protests/) it to Belarusian-style repression. Georgian Dream Prime Minister Irakli Kobakhidze defended the move as necessary to close legislative “loopholes” and strengthen state control. Journalists and activists warn that the law is part of a broader crackdown on press freedom and dissent. Decentralized social networks like Nostr will become increasingly vital for journalists and activists to communicate freely, resist censorship, and ensure the flow of independent information.
\___________________________________________________________\_
#### **Webinar Series for Nonprofits: Become Unstoppable**
HRF will host a [free, three-day webinar](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform) from March 17-19, teaching human rights defenders and nonprofits how to use Bitcoin to counter state censorship and confiscation. Sessions run daily from 10:30 a.m. to 12:00 p.m. EDT and are beginner-friendly. The webinar will be led by Anna Chekhovich, HRF’s Bitcoin nonprofit adoption lead and financial manager at Alexei Navalny’s Anti-Corruption Foundation.
### [Register Here](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform)
#### **SXSW | The Human Rights Risks of Central Bank Digital Currencies (CBDCs)**
Join HRF at [SXSW 2025](https://www.sxsw.com/) in Austin from March 9-12 to explore how CBDCs threaten financial freedom. Experts [Roger Huang](https://x.com/Rogerh1991), [Charlene Fadirepo](https://x.com/CharFadirepo), and [Nick Anthony](https://x.com/EconWithNick) will discuss how authoritarian regimes use CBDCs for surveillance and control on March 9. Attendees can also visit HRF’s [CBDC Tracker](https://cbdctracker.hrf.org/) booth to explore an interactive map of CBDC developments worldwide.
### [Get Tickets](https://www.sxsw.com/conference/)
\___________________________________________________________\_
## BITCOIN AND FREEDOM TECH NEWS
#### **Mullvad VPN | Testing Lightning Network Payments**
[Mullvad VPN](https://mullvad.net/en) is experimenting with Bitcoin for payments via the Lightning Network, a second-layer payment protocol built on Bitcoin that enables faster, cheaper, and more private transactions. This integration lets Mullvad VPN users pay for their services in bitcoin while enhancing their privacy and bypassing payment networks that track or censor financial activity. VPNs protect users by masking IP addresses and encrypting traffic. Accepting Bitcoin over Lightning strengthens this protection with a censorship-resistant payment option. For activists, journalists, and individuals in authoritarian regimes, this combination provides a shield against surveillance.
#### **SeedSigner | Releases Multilingual Support**
[SeedSigner](https://seedsigner.com/), an open-source and customizable Bitcoin hardware wallet and HRF grantee, [introduced](https://github.com/SeedSigner/seedsigner/releases/tag/0.8.5) multilingual support for Spanish. This update makes secure Bitcoin self-custody more accessible to Spanish-speaking activists and human rights defenders who may rely on Bitcoin for transactional freedom. By expanding access to secure self-custody, SeedSigner helps reduce dependence on restrictive financial systems and allows more people in Nicaragua, Venezuela, Cuba, and beyond to “be their own bank.”
#### **Iris | Implements Private Bitcoin Payments with Cashu**
[Iris](https://iris.cx/), a Nostr client, has added support for a Cashu wallet to allow users to send and receive ecash. Cashu is an open-source Chaumian ecash protocol built for Bitcoin and integrated with the Lightning Network. It lets users make fast, low-cost, and extremely private transactions using Bitcoin-backed ecash. While it requires a trusted custodian, it helps users spend Bitcoin anonymously without revealing their identity or transaction activity. This ability provides activists and nonprofits a different way to make private Bitcoin payments alongside nostr’s censorship-resistant communications.
#### **Sparrow Wallet | Supports Lark for USB Hardware Wallets**
[Sparrow Wallet](https://sparrowwallet.com/), a popular open-source Bitcoin wallet, has added support for [Lark](https://github.com/sparrowwallet/larkapp?mc_cid=aab08acf41&mc_eid=5c5878c08e), a new tool for USB hardware wallet communication. Lark works alongside the existing [Hardware Wallet Interface](https://github.com/bitcoin-core/HWI) (HWI), giving users an alternative way to connect their hardware wallets via USB. This update improves reliability, reduces dependence on a single software interface, and strengthens Bitcoin self-custody.
#### **Bitcoin Dada | Opens Applications for Second Cohort of Dada Devs**
[Bitcoin Dada](https://btcdada.com/), an HRF-supported nonprofit initiative empowering African women through Bitcoin and financial education, is now [accepting](https://x.com/DadaDevs/status/1886819762660929674) applications for the second cohort of Dada Devs. This developer program provides hands-on training, mentorship, and a collaborative community to help African women under authoritarian regimes contribute to Bitcoin development. If you’re an aspiring female developer, [apply now](https://docs.google.com/forms/d/e/1FAIpQLSeJ8nXL96qNeCAaXnSlGxqykBPEGm21z9qS9oE1ldNusM0nTA/viewform) to join a network of African women shaping the future of finance. Applications close Feb. 13.
#### **Summer of Bitcoin | Applications for Summer 2025 Cohort Now Open**
[Summer of Bitcoin](https://www.summerofbitcoin.org/), an HRF-supported Bitcoin internship program, is now accepting [applications](https://www.summerofbitcoin.org/apply) for its summer 2025 cohort. This program introduces students from anywhere, including from authoritarian regimes, to Bitcoin open-source development and design, giving interns the option to choose between a developer or designer track based on their interests. Participants will gain hands-on work experience, contribute to real-world Bitcoin projects, and receive mentorship from industry leaders. You can learn more and apply [here](https://www.summerofbitcoin.org/).
#### **Spiral | Announces Grant Renewals for the Bitcoin Design Community and BDK**
[Spiral](http://spiral.xyz), a Bitcoin company building and funding open-source projects, announced renewed grants for critical initiatives, including the [Bitcoin Design Community](https://github.com/bitcoindesign) and [Bitcoin Dev Kit](https://bitcoindevkit.org/) (BDK). The Bitcoin Design Community is a free and open-source resource for designers, developers, and others working on non-custodial Bitcoin products. This [grant](https://x.com/spiralbtc/status/1885000120439095607) will support designers who push the user experience and adoption of Bitcoin forward. Meanwhile, BDK is a software library that helps developers in building cross-platform Bitcoin wallets. Its [grant](https://x.com/spiralbtc/status/1884998758976405840) will support the project’s continued refinement and development.
## RECOMMENDED CONTENT
#### **The Bitcoin and Cypherpunk Spirit Is Alive and Well in Africa by Frank Corva**
In this [article](https://bitcoinmagazine.com/culture/the-bitcoin-and-cypherpunk-spirit-is-alive-and-well-in-africa) for [Bitcoin Magazine](http://bitcoinmagazine.com), journalist [Frank Corva](https://x.com/frankcorva) spotlights Bitcoin's growing presence across Africa. Across the continent, people are building Bitcoin circular economies, open-source financial tools, and educational initiatives. From [Bitcoin Ekasi](https://x.com/BitcoinEkasi) in South Africa to [AfriBit Kibera](https://x.com/AfribitKibera) in Kenya and [Bitcoin Dua](https://x.com/bitcoin_dua) in Ghana, these grassroots initiatives drive financial inclusion and education for individuals and communities. Meanwhile, tools like [Tando](https://tando.me/) and [Machankura](https://8333.mobi/) are expanding access to transactional freedom, and conferences like [Adopting Bitcoin Captetown](https://za25.adoptingbitcoin.org/) and the [Africa Bitcoin Conference](https://afrobitcoin.org/) nurture ongoing collaboration between individuals, developers, and activists to advance financial freedom on a continent that otherwise has very little liberal democracy. Read the full article [here](https://bitcoinmagazine.com/culture/the-bitcoin-and-cypherpunk-spirit-is-alive-and-well-in-africa).
#### **Using Bitcoin Without Internet! Here’s How Machankura Makes It Happen with Anita Posch**
In this short [interview](https://www.youtube.com/watch?v=XzXfd237XVo), Bitcoin educator and host of the [Bitcoin for Fairness](https://www.youtube.com/@AnitaPosch) channel, Anita Posch, speaks with Mary Imasuen, a [Machankura](https://8333.mobi/) team member, about how this technology makes Bitcoin accessible to Africans without Internet access. Machankura is an app that allows feature phones to send and receive Bitcoin using the Unstructured Supplementary Service Data (USSD) protocol, a mobile communications system similar to SMS. This means people can transact in Bitcoin without needing a smartphone or data connection, a situation common to many living under autocratic regimes in sub-Saharan Africa. By removing Internet barriers, Machankura helps millions of Africans overcome high data costs and unreliable networks, offering a practical solution to financial inclusion.
*If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).*
*Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\
*Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)*
*The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*.
[**Subscribe to newsletter**](http://financialfreedomreport.org/)
[**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Visit our website**](https://hrf.org/programs/financial-freedom/)
-

@ 1c197b12:242e1642
2025-02-09 22:56:33
A Cypherpunk's Manifesto
by Eric Hughes
Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world.
If two parties have some sort of dealings, then each has a memory of their interaction. Each party can speak about their own memory of this; how could anyone prevent it? One could pass laws against it, but the freedom of speech, even more than privacy, is fundamental to an open society; we seek not to restrict any speech at all. If many parties speak together in the same forum, each can speak to all the others and aggregate together knowledge about individuals and other parties. The power of electronic communications has enabled such group speech, and it will not go away merely because we might want it to.
Since we desire privacy, we must ensure that each party to a transaction have knowledge only of that which is directly necessary for that transaction. Since any information can be spoken of, we must ensure that we reveal as little as possible. In most cases personal identity is not salient. When I purchase a magazine at a store and hand cash to the clerk, there is no need to know who I am. When I ask my electronic mail provider to send and receive messages, my provider need not know to whom I am speaking or what I am saying or what others are saying to me; my provider only need know how to get the message there and how much I owe them in fees. When my identity is revealed by the underlying mechanism of the transaction, I have no privacy. I cannot here selectively reveal myself; I must always reveal myself.
Therefore, privacy in an open society requires anonymous transaction systems. Until now, cash has been the primary such system. An anonymous transaction system is not a secret transaction system. An anonymous system empowers individuals to reveal their identity when desired and only when desired; this is the essence of privacy.
Privacy in an open society also requires cryptography. If I say something, I want it heard only by those for whom I intend it. If the content of my speech is available to the world, I have no privacy. To encrypt is to indicate the desire for privacy, and to encrypt with weak cryptography is to indicate not too much desire for privacy. Furthermore, to reveal one's identity with assurance when the default is anonymity requires the cryptographic signature.
We cannot expect governments, corporations, or other large, faceless organizations to grant us privacy out of their beneficence. It is to their advantage to speak of us, and we should expect that they will speak. To try to prevent their speech is to fight against the realities of information. Information does not just want to be free, it longs to be free. Information expands to fill the available storage space. Information is Rumor's younger, stronger cousin; Information is fleeter of foot, has more eyes, knows more, and understands less than Rumor.
We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.
We the Cypherpunks are dedicated to building anonymous systems. We are defending our privacy with cryptography, with anonymous mail forwarding systems, with digital signatures, and with electronic money.
Cypherpunks write code. We know that someone has to write software to defend privacy, and since we can't get privacy unless we all do, we're going to write it. We publish our code so that our fellow Cypherpunks may practice and play with it. Our code is free for all to use, worldwide. We don't much care if you don't approve of the software we write. We know that software can't be destroyed and that a widely dispersed system can't be shut down.
Cypherpunks deplore regulations on cryptography, for encryption is fundamentally a private act. The act of encryption, in fact, removes information from the public realm. Even laws against cryptography reach only so far as a nation's border and the arm of its violence. Cryptography will ineluctably spread over the whole globe, and with it the anonymous transactions systems that it makes possible.
For privacy to be widespread it must be part of a social contract. People must come and together deploy these systems for the common good. Privacy only extends so far as the cooperation of one's fellows in society. We the Cypherpunks seek your questions and your concerns and hope we may engage you so that we do not deceive ourselves. We will not, however, be moved out of our course because some may disagree with our goals.
The Cypherpunks are actively engaged in making the networks safer for privacy. Let us proceed together apace.
Onward.
Eric Hughes <hughes@soda.berkeley.edu>
9 March 1993
-

@ 9673b322:1b75ee9e
2025-02-13 14:15:38
This is test content

-

@ dc4cd086:cee77c06
2025-02-09 03:35:25
Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content.
## Key Features:
### Video Processing:
- Automatically downloads YouTube videos, transcripts, and chapter information
- Splits transcripts into sections based on video chapters
### Content Summarization:
- Utilizes language models to transform spoken content into clear, readable text
- Formats output in AsciiDoc for improved readability and navigation
- Highlights key terms and concepts with [[term]] notation for potential cross-referencing
### Diagram Extraction:
- Analyzes video entropy to identify static diagram/slide sections
- Provides a user-friendly GUI for manual selection of relevant time ranges
- Allows users to pick representative frames from selected ranges
## Going Forward:
Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine.
Will support multiple open and closed language models for user choice
Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care.
While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs.
## Screenshots
### Frame Selection

This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection.
### Diagram Extraction

This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save.
## Links
- repo: https://github.com/limina1/video_article_converter
- Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE
## Output
And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately.
You can now view the article on #Alexandria
https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101
Initially published as chained kind 1's
nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn
Or view on Coracle
https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
-

@ 9673b322:1b75ee9e
2025-02-13 14:10:06
This is some test content
Adding a Sample Image

-

@ 2e8970de:63345c7a
2025-02-13 13:39:35
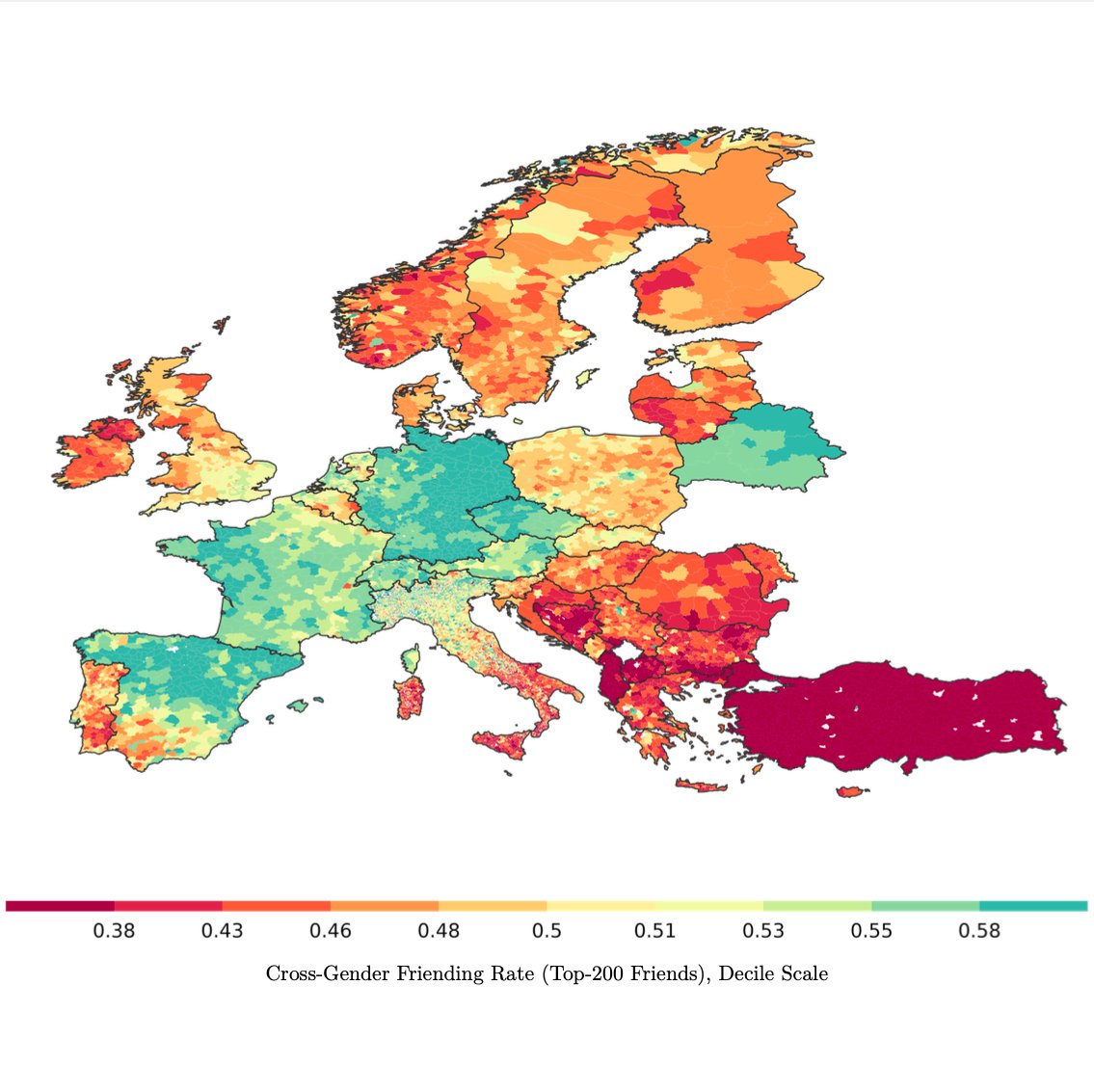
> We measure gender differences using the Cross-Gender Friending Ratio, the ratio of female friends in men's networks to the share of female friends in women's networks in a given place.
Men almost always have a lower share of female friends than women do, but the degree varies:
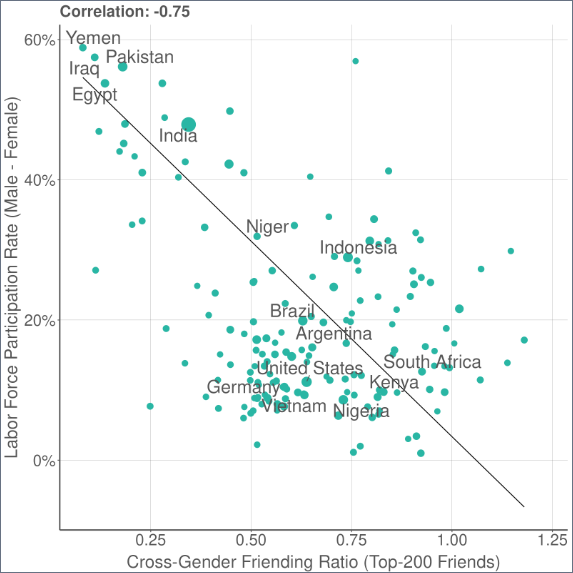
> Across countries, the CGFR is strongly predictive of gender differences in labor force participation.
Within countries, we also find a strong correlation with gender attitudes in the World Values Survey, such as beliefs about women's suitability for politics.
https://x.com/drew_m_johnston/status/1889794718004826288
originally posted at https://stacker.news/items/884660
-

@ 32e18276:5c68e245
2025-02-08 20:20:46
This period of the Damus OpenSats grant has been productive, and encompasses the work past our alpha release of Notedeck. Since we sent our last report on Dec 5, this encompasses all the work after then.
Damus is supported by the OpenSats LTS grant, which allows us to continue working on the goodies below. Thank you!
## Damus Notedeck
### Added
- Initial algo timelines (William Casarin) [#712](https://github.com/damus-io/notedeck/pull/712)
- Initial support for local-network P2P nostr: multicast support (William Casarin) [#626](https://github.com/damus-io/notedeck/pull/626)
- First steps toward the notedeck browser: multiple app support [#565](https://github.com/damus-io/notedeck/pull/565)
- Clicking a mention now opens profile page (William Casarin) [5a241d730](https://github.com/damus-io/notedeck/commit/5a241d730e3d83f8057e211485edfde2f3c96e54)
- Note previews when hovering reply descriptions (William Casarin) [#591](https://github.com/damus-io/notedeck/pull/591)
- Various Android updates and compatibility improvements (Ken Sedgwick, William Casarin)
- Media uploads (kernelkind) [#662](https://github.com/damus-io/notedeck/pull/662)
- Profile editing (kernelkind) [#625](https://github.com/damus-io/notedeck/pull/625)
- Add hashtags to posts (Daniel Saxton) [#592](https://github.com/damus-io/notedeck/pull/592)
- Enhanced command-line interface for user interactions (Ken Sedgwick)
- Debug features for user relay-list and mute list synchronization (Ken Sedgwick)
### Changed
- Major timeline cache refactor (William Casarin) [#653](https://github.com/damus-io/notedeck/pull/653)
- Increased ping intervals for network performance (William Casarin)
- Migrated to egui v0.29.1 (William Casarin) [#551](https://github.com/damus-io/notedeck/pull/551)
- Switch to only notes & replies on some tabs (William Casarin) [#598](https://github.com/damus-io/notedeck/pull/598)
- Only show column delete button when not navigating (William Casarin)
- Pointer interactions enhancements in UI (William Casarin)
- Show profile pictures in column headers (William Casarin)
- Show usernames in user columns (William Casarin)
- Add confirmation when deleting columns (kernelkind)
- Enhance Android build and performance (Ken Sedgwick)
- Image cache handling using sha256 hash (kieran)
- Introduction of decks_cache and improvements (kernelkind)
- Nostrdb update for async support (Ken Sedgwick)
- Persistent theme setup across sessions (kernelkind)
- Tombstone muted notes (Ken)
### Fixed
- Fix GIT_COMMIT_HASH compilation issue (William Casarin)
- Fix avatar alignment in profile previews (William Casarin)
- Fix broken quote repost hitbox (William Casarin)
- Fix crash when navigating in debug mode (William Casarin)
- Fix long delays when reconnecting (William Casarin)
- Fix repost button size (William Casarin)
- Fixed since kind filters (kernelkind)
- Clippy warnings resolved (Dimitris Apostolou)
## Damus iOS
Work continued on the iOS side. While I was not directly involved in the work since the last report, I have been directing and managing its development.
### Added
- Render Gif and video files while composing posts (Swift Coder)
- Purple members who have been active for more than a year now get a special badge (Daniel D’Aquino)
- Add profile info text in stretchable banner with follow button (Swift Coder)
- Paste Gif image similar to jpeg and png files (Swift Coder)
### Changed
- Improved clarity of the mute button to indicate it can be used for blocking a user (Daniel D’Aquino)
- Made the microphone access request message more clear to users (Daniel D’Aquino)
- Improved UX around the label for searching words (Daniel D’Aquino)
- Improved accessibility support on some elements (Daniel D’Aquino)
### Fixed
- Fixed issue where the "next" button would appear hidden and hard to click on the create account view (Daniel D’Aquino)
- Fix non scrollable wallet screen (Swift Coder)
- Fixed suggested users category titles to be localizable (Terry Yiu)
- Fixed GradientFollowButton to have consistent width and autoscale text limited to 1 line (Terry Yiu)
- Fixed right-to-left localization issues (Terry Yiu)
- Fixed AddMuteItemView to trim leading and trailing whitespaces from mute text and disallow adding text with only whitespaces (Terry Yiu)
- Fixed SideMenuView text to autoscale and limit to 1 line (Terry Yiu)
- Fixed an issue where a profile would need to be input twice in the search to be found (Daniel D’Aquino)
- Fixed non-breaking spaces in localized strings (Terry Yiu)
- Fixed localization issue on Add mute item button (Terry Yiu)
- Replace non-breaking spaces with regular spaces as Apple's NSLocalizedString macro does not seem to work with it (Terry Yiu)
- Fixed localization issues in RelayConfigView (Terry Yiu)
- Fix duplicate uploads (Swift Coder)
- Remove duplicate pubkey from Follow Suggestion list (Swift Coder)
- Fix Page control indicator (Swift Coder)
- Fix damus sharing issues (Swift Coder)
- Fixed issue where banner edit button is unclickable (Daniel D’Aquino)
- Handle empty notification pages by displaying suitable text (Swift Coder)
## Nostrdb
nostrdb, the engine that powers [notecrumbs](https://github.com/damus-io/notecrumbs), damus iOS, and notedeck, continued to improve:
### Added
- Added nip50 fulltext searching (William Casarin) [#68](https://github.com/damus-io/nostrdb/pull/68), [demo](nostr:nevent1qqsp3rx83t5h0vdhu4txru76uycfnaegfj3wg6wncamkarcnrccssvcpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqvhpsfmr23gwhv795lgjc8uw0v44z3pe4sg2vlh08k0an3wx3cj9efqkkv)
- Added async migrations (William Casarin) [#59](https://github.com/damus-io/nostrdb/pull/59)
- Implement author queries (William Casarin) [#57](https://github.com/damus-io/nostrdb/pull/57)
- Make `ndb` threadsafe (William Casarin) [#56](https://github.com/damus-io/nostrdb/pull/56)
## Nostrdb Rust
Our nostrdb rust bindings also had improvements
- Async! Adding efficient, poll-based stream support (William Casarin): [#25](https://github.com/damus-io/nostrdb-rs/pull/25)
## Notecrumbs
Notecrumbs, the njump-style opengraph server that powers the damus.io links, got an update that upgraded it to async nostrdb
- Switch to async nostrdb-rs (William Casarin) [#16](https://github.com/damus-io/notecrumbs/pull/16)
## How money was used
- relay.damus.io server costs
- Living expenses
## Next quarter
Our goal for next update: zaps, android version, lists, outbox model for notedeck. Olas images in damus iOS, continue switching Damus iOS over to local relay model so we can add outbox support.
-

@ c2827524:5f45b2f7
2025-02-13 11:54:16
> innèsto s. m. [der. di innestare]. – 1. In agraria: a. Operazione con cui si fa concrescere sopra una pianta (detta portainnesto o soggetto) una parte di un altro della stessa specie o di specie differenti (detto nesto o oggetto), **al fine di formare un nuovo individuo più pregiato o più produttivo o più giovane**: fare, operare, praticare un innesto.
Le collaborazioni sono di una potenza micidiale.
Quelle che si sviluppano nello spazio #Bitcoin ancora di più.
Non è più una collaborazione, è un #innesto: rami di alberi diversi, destinati da soli a dare grandi frutti, si fondono per **donare ad un intero ecosistema sapori ancora più deliziosi**.
Contributi e suggerimenti vanno e vengono alla velocità della luce, col sorriso, senza sacrificio e sempre con la volontà di migliorarsi e crescere.
Lo spazio #Bitcoin è una fabbrica magica, che accoglie minuscoli semini(*) da chiunque voglia partecipare, volontariamente, alla crescita della cultura Bitcoin. Ma li trasforma in un **incanto**.
In solitaria i semini sarebbero destinati comunque a grandi cose e questo è già, di per sé, meraviglioso. La fabbrica magica, invece, li fa germogliare, fiorire e fruttare in maniera ancora più potente.
Quando la magia è totale, avviene l’*innesto*, **la generazione di una nuova creatura più pregiata**.
Sta succedendo davanti ai miei occhi. Sono onorata di poter assistere a questo mini miracolo della vita e, manco a dirlo, felice di farne parte.
Non è solo cambiare atteggiamento, smussare frizioni e rigidità o correggere la propria visione, è proprio ampliare sé stessi accogliendo gli altri.
Grazie nostr:npub1uhj92lnwh8rrhhuvulfqstk4g0ayx0zx35wj2d62jueqheknkxks5m4zj6 nostr:npub1au23c73cpaq2whtazjf6cdrmvam6nkd4lg928nwmgl78374kn29sq9t53j nostr:npub1awnu9vg352863e7tqlc6urlw7jgdf8vf00tmr76uuhflp4nnn68sjmnnl3 e nostr:npub1lrurmgmlfl4u72258fc4q5ke7tr82kw5xct5vchdmzr9uhmx6j4qn3t72a
(1) Semini, non #seed [non chiamatelo seed, si dice mnemonica (cit.)]
Siccome in italiano la parola **seme** porta alla mente anche *giochini di parole fiat*, se siete qui per perculare fate pure. -> H.F.S.P. 🤣
-

@ e5de231a:958477f6
2025-02-13 11:32:41
Market Insights:
Advanced Semiconductor Packaging Market Size was valued at USD 37.90 Billion in 2024. The Advanced Semiconductor Packaging Market industry is projected to grow from USD 40.94 Billion in 2025 to USD 81.85 Billion by 2034, exhibiting a compound annual growth rate (CAGR) of 8.0% during the forecast period (2025 - 2034). The integration of semiconductor components in vehicles will fuel the global semiconductor advanced packaging market growth. The electrification of automobiles as well as the rising demand for automation in vehicles are expected to be a significant market driver for the Advanced Semiconductor Packaging Market.
In the dynamic landscape of technological advancements, the semiconductor industry stands at the forefront, steering innovation and progress. The [Advanced Semiconductor Packaging Market](https://www.marketresearchfuture.com/reports/advanced-semiconductor-packaging-market-12505), a crucial facet of this realm, plays a pivotal role in shaping the future of electronic devices. In this comprehensive exploration, we delve into the intricacies of this market, unraveling its complexities and forecasting its trajectory.
Understanding the Essence of Advanced Semiconductor Packaging
What Sets Advanced Semiconductor Packaging Apart?
Semiconductor packaging is the art and science of protecting and enhancing semiconductor devices, ensuring optimal performance in electronic applications. As technology evolves, the demand for more efficient, compact, and powerful semiconductor packaging solutions has surged. This is where the 'advanced' in Advanced Semiconductor Packaging becomes a game-changer.
Miniaturization and Integration: The driving force behind advanced packaging lies in the quest for smaller, yet more potent, electronic components. The market is witnessing a paradigm shift towards compact designs without compromising on functionality.
Heterogeneous Integration: Combining diverse materials and technologies into a single package is the hallmark of advanced semiconductor packaging. This amalgamation fosters improved performance, energy efficiency, and overall system reliability.
Enhanced Thermal Management: As electronic devices become more powerful, managing heat dissipation becomes a critical challenge. Advanced packaging solutions incorporate innovative thermal management techniques to ensure sustained high performance.
Market Trends and Projections
Riding the Waves of Innovation
5G Integration: The advent of 5G technology has propelled the need for advanced semiconductor packaging to new heights. The market is witnessing a surge in demand for packaging solutions that can support the high-frequency requirements of 5G-enabled devices.
Artificial Intelligence (AI) Integration: AI-driven applications demand robust semiconductor solutions. Advanced packaging, with its focus on efficient power delivery and heat dissipation, aligns perfectly with the requirements of AI-powered devices.
Automotive Electronics: The automotive industry's shift towards electric and autonomous vehicles has fueled the demand for advanced semiconductor packaging. These packages need to withstand harsh environments while delivering exceptional performance.
Market Dynamics and Key Players
The Advanced Semiconductor Packaging Market is characterized by intense competition and rapid technological advancements. Key players in this landscape include:
Intel Corporation: A pioneer in semiconductor technology, Intel continues to lead the market with innovations in packaging solutions.
Advanced Micro Devices (AMD): Renowned for its cutting-edge processors, AMD's foray into advanced packaging has added a new dimension to the market.
Taiwan Semiconductor Manufacturing Company (TSMC): As a global semiconductor manufacturing giant, TSMC's influence on the market is undeniable, shaping the industry's future through advanced packaging technologies.
Challenges and Future Prospects
Navigating the Road Ahead
While the Advanced Semiconductor Packaging Market is poised for growth, it is not without its challenges:
Complexity of Integration: As technologies converge, integrating diverse components into a single package poses significant technical challenges.
Supply Chain Disruptions: The global semiconductor shortage has underscored the vulnerability of the supply chain. Addressing these disruptions is crucial for sustained market growth.
Environmental Considerations: The semiconductor industry is under increasing scrutiny for its environmental impact. Sustainable packaging solutions and responsible manufacturing practices are becoming paramount.
Related Reports:
[Super Capacitors Energy Storage System Market](https://www.marketresearchfuture.com/reports/super-capacitors-battery-energy-storage-system-market-1158)
[Interactive Whiteboard Market](https://www.marketresearchfuture.com/reports/interactive-whiteboard-market-6087)
Conclusion
In conclusion, the Advanced Semiconductor Packaging Market is a dynamic arena where innovation converges with necessity. As we navigate the complexities of an interconnected world, the role of advanced packaging in shaping the future of electronics cannot be overstated. The market's trajectory is marked by challenges, but also by unprecedented opportunities for those at the forefront of technological evolution.
-

@ d57360cb:4fe7d935
2025-02-06 18:31:30
Mindfulness often has the misconception that by practicing you can stop your mind from thinking and obtain an empty mind.
While one can definitely achieve moments of emptiness in thinking, this view that emptiness is the goal can be the very obstacle in your way leading to frustration with the practice.
If we adjust our perspective and see mindfulness as learning to accept the situations we find ourselves in and adjust to them rather than fighting them, we achieve a kind of grace under pressure.
The thoughts are part of the practice, just like cars on the road are part of driving, or the danger of a punch is always a threat to a boxer.
The difference between the novice and the seasoned is one has accepted and acclimated to the realities of the situation instead of fighting them, in this one finds freedom.
-

@ d360efec:14907b5f
2025-02-13 11:15:12
**Top-Down Analysis:** กลยุทธ์การเทรดเพื่อมองภาพรวมและจับจังหวะทำกำไร
ในโลกของการเทรดที่เต็มไปด้วยความผันผวน การมีเครื่องมือวิเคราะห์ที่แข็งแกร่งเป็นสิ่งสำคัญอย่างยิ่งที่จะช่วยนำทางให้เทรดเดอร์สามารถตัดสินใจได้อย่างมีหลักการและเพิ่มโอกาสในการทำกำไร หนึ่งในเครื่องมือที่ได้รับความนิยมและมีประสิทธิภาพคือ "Top-Down Analysis" หรือการวิเคราะห์จากบนลงล่าง ซึ่งเป็นวิธีการมองภาพรวมของตลาดก่อนที่จะเจาะจงไปที่สินทรัพย์ที่เราสนใจ บทความนี้จะพาคุณไปทำความเข้าใจกับ Top-Down Analysis อย่างละเอียด พร้อมทั้งแนะนำกลยุทธ์การเทรดที่สามารถนำไปปรับใช้ได้จริง
**Top-Down Analysis คืออะไร?**
Top-Down Analysis เป็นกระบวนการวิเคราะห์ตลาดที่เริ่มต้นจากการพิจารณาภาพรวมในกรอบเวลาที่ใหญ่ขึ้น ก่อนที่จะค่อยๆ ย่อยลงไปในกรอบเวลาที่เล็กลง เพื่อทำความเข้าใจบริบทของตลาดและหาจังหวะการเทรดที่เหมาะสม วิธีการนี้ช่วยให้เทรดเดอร์สามารถมองเห็นทิศทางหลักของตลาด, แนวโน้มที่กำลังเกิดขึ้น, ระดับราคาสำคัญ, และความสมดุลระหว่างอุปสงค์และอุปทาน ก่อนที่จะตัดสินใจเข้าเทรดในกรอบเวลาที่เล็กลง
**องค์ประกอบสำคัญของ Top-Down Analysis (อ้างอิงจากภาพ)**
ภาพ "Top-Down Analysis" ได้สรุปองค์ประกอบสำคัญของการวิเคราะห์นี้ไว้อย่างชัดเจน โดยแบ่งการวิเคราะห์ออกเป็น 3 กรอบเวลาหลัก: 4 ชั่วโมง (4H), 1 ชั่วโมง (1H), และ 15 นาที (15min) แต่ละกรอบเวลามีองค์ประกอบที่ต้องพิจารณาดังนี้:
1. กรอบเวลา 4 ชั่วโมง (4H): ภาพรวมตลาดและทิศทางหลัก
ในกรอบเวลา 4 ชั่วโมง เราจะเน้นการวิเคราะห์ภาพรวมของตลาด เพื่อกำหนดทิศทางหลักและแนวโน้มในระยะกลาง องค์ประกอบสำคัญในกรอบเวลานี้คือ:
* Direction (ทิศทาง): ประเมินทิศทางที่ตลาดกำลังเคลื่อนที่ไป โดยพิจารณาจากแนวโน้มและโครงสร้างราคาในภาพรวม ตลาดกำลังเป็นขาขึ้น, ขาลง หรืออยู่ในช่วง Sideways?
* Trend (แนวโน้ม): ระบุแนวโน้มหลักของตลาด ไม่ว่าจะเป็นแนวโน้มขาขึ้น (Uptrend), แนวโน้มขาลง (Downtrend) หรือ Sideways การเข้าใจแนวโน้มช่วยในการกำหนดกลยุทธ์การเทรดที่เหมาะสม
* Key levels (ระดับราคาสำคัญ): หาระดับราคาแนวรับและแนวต้านที่สำคัญในกรอบเวลา 4 ชั่วโมง ระดับเหล่านี้มักเป็นจุดที่ราคาเคยมีการกลับตัวหรือพักตัวในอดีต และอาจเป็นบริเวณที่ราคาจะตอบสนองอีกครั้งในอนาคต
* Supply & Demand (อุปทานและอุปสงค์): วิเคราะห์ความสมดุลระหว่างแรงซื้อ (Demand) และแรงขาย (Supply) ในตลาด โดยพิจารณาจากพฤติกรรมราคาบริเวณแนวรับแนวต้าน และสัญญาณจากเครื่องมือวิเคราะห์อื่นๆ (ถ้าใช้)
2. กรอบเวลา 1 ชั่วโมง (1H): หาจังหวะและบริเวณที่น่าสนใจ
เมื่อได้ภาพรวมและทิศทางหลักจากกรอบ 4H แล้ว เราจะย่อยลงมาในกรอบ 1 ชั่วโมง เพื่อหาจังหวะการเทรดที่สอดคล้องกับทิศทางหลัก และมองหารูปแบบราคาที่น่าสนใจ องค์ประกอบสำคัญในกรอบเวลานี้คือ:
* Breaks (การทะลุ): สังเกตการทะลุแนวรับแนวต้าน หรือระดับราคาสำคัญในกรอบ 1H ที่สอดคล้องกับทิศทางหลักใน 4H การทะลุเหล่านี้อาจเป็นสัญญาณของการเคลื่อนไหวครั้งใหญ่ของราคา
* Reversals (การกลับตัว): มองหารูปแบบการกลับตัวของราคาที่อาจเกิดขึ้นบริเวณระดับราคาสำคัญในกรอบ 1H ซึ่งบ่งบอกถึงจุดสิ้นสุดของแนวโน้มปัจจุบันและเริ่มต้นแนวโน้มใหม่
* OB (Order Blocks): ระบุบริเวณ Order Blocks ในกรอบ 1H ซึ่งเป็นพื้นที่ที่มีการสั่งซื้อขายจำนวนมากในอดีต Order Blocks เหล่านี้มักจะทำหน้าที่เป็นแนวรับแนวต้านในอนาคต
* FVG (Fair Value Gaps): มองหา Fair Value Gaps ในกรอบ 1H ซึ่งเป็นช่องว่างของราคาที่เกิดจากการเคลื่อนไหวอย่างรวดเร็ว FVG มักจะเป็นเป้าหมายของราคาในอนาคต เนื่องจากราคาอาจจะกลับมาปิดช่องว่างเหล่านี้
* Liquidity (สภาพคล่อง): ประเมินสภาพคล่องบริเวณระดับราคาที่เราสนใจในกรอบ 1H บริเวณที่มีสภาพคล่องสูงมักจะดึงดูดนักลงทุนรายใหญ่ และอาจทำให้เกิดการเคลื่อนไหวของราคาที่รุนแรง
3. กรอบเวลา 15 นาที (15min): ยืนยันสัญญาณและหาจุดเข้าเทรด
ในกรอบเวลา 15 นาที เราจะเน้นการยืนยันสัญญาณการเทรด และหาจุดเข้าเทรดที่แม่นยำ เพื่อลดความเสี่ยงในการเข้าเทรดเร็วเกินไป องค์ประกอบสำคัญในกรอบเวลานี้คือ:
* Confirmation (การยืนยัน): รอสัญญาณยืนยันการเคลื่อนไหวของราคาในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบ 1H และ 4H สัญญาณยืนยันอาจมาในรูปแบบของแท่งเทียนกลับตัว, รูปแบบ Chart Patterns, หรือสัญญาณจาก Indicators
* จุดเข้าเทรด: เมื่อมีสัญญาณยืนยันที่ชัดเจนในกรอบ 15 นาที และสอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น จึงตัดสินใจเข้าเทรด โดยกำหนด Stop Loss เพื่อจำกัดความเสี่ยง และ Take Profit เพื่อตั้งเป้าหมายในการทำกำไร
**กลยุทธ์การเทรด Top-Down Analysis: ขั้นตอนสู่ความสำเร็จ**
เพื่อนำ Top-Down Analysis ไปใช้ในการเทรดอย่างมีประสิทธิภาพ เราสามารถทำตามขั้นตอนต่อไปนี้:
1. **เริ่มต้นที่ 4H**: กำหนดทิศทางและแนวโน้มหลัก วิเคราะห์กราฟ 4H เพื่อระบุทิศทางหลักของตลาด แนวโน้ม และระดับราคาสำคัญ ประเมินความสมดุลของ Supply & Demand เพื่อกำหนด Bias การเทรด (เน้นซื้อหรือขาย)
2. **เจาะลึก 1H:** หาจังหวะและบริเวณที่น่าสนใจ เมื่อได้ทิศทางหลักจาก 4H แล้ว ให้ย่อยลงมาดูกราฟ 1H เพื่อหารูปแบบราคาที่น่าสนใจ เช่น การทะลุแนวรับแนวต้าน, รูปแบบการกลับตัว, Order Blocks, Fair Value Gaps และบริเวณที่มีสภาพคล่องสูง
3. **ยืนยันใน 15min:** หาจุดเข้าเทรดที่แม่นยำ รอสัญญาณยืนยันในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น ใช้ Price Action, แท่งเทียน, หรือ Indicators เพื่อยืนยันสัญญาณ และหาจุดเข้าเทรดที่แม่นยำ พร้อมกำหนด Stop Loss และ Take Profit ที่เหมาะสม
**ประโยชน์ของการใช้ Top-Down Analysis**
* มองเห็นภาพรวมตลาด: ช่วยให้เทรดเดอร์เข้าใจบริบทของตลาดในภาพรวม ไม่หลงทางในรายละเอียดเล็กๆ น้อยๆ
* ตัดสินใจเทรดอย่างมีหลักการ: ทำให้การตัดสินใจเทรดมีเหตุผลและมีข้อมูลสนับสนุนมากขึ้น ไม่ใช่แค่การคาดเดา
* เพิ่มความแม่นยำในการเทรด: การวิเคราะห์หลายกรอบเวลาช่วยกรองสัญญาณรบกวน และเพิ่มโอกาสในการเข้าเทรดในทิศทางที่ถูกต้อง
* ลดความเสี่ยง: ช่วยลดโอกาสในการเทรดสวนทางแนวโน้มหลักของตลาด และช่วยในการกำหนด Stop Loss ที่เหมาะสม
**ข้อควรจำและข้อควรระวัง**
* ฝึกฝนและสังเกต: Top-Down Analysis ต้องอาศัยการฝึกฝนและการสังเกตกราฟราคาอย่างสม่ำเสมอ เพื่อพัฒนาความเข้าใจและทักษะในการวิเคราะห์
* ปรับใช้ให้เข้ากับสไตล์: ปรับกลยุทธ์ให้เข้ากับสไตล์การเทรดของคุณ และสินทรัพย์ที่คุณเทรด
* บริหารความเสี่ยง: ให้ความสำคัญกับการบริหารความเสี่ยงเสมอ กำหนดขนาด Position ที่เหมาะสม และใช้ Stop Loss ทุกครั้ง
* ไม่มีกลยุทธ์ใดสมบูรณ์แบบ: Top-Down Analysis เป็นเครื่องมือที่มีประสิทธิภาพ แต่ไม่มีกลยุทธ์ใดที่รับประกันผลกำไร 100% การเทรดมีความเสี่ยง โปรดศึกษาและทำความเข้าใจความเสี่ยงก่อนตัดสินใจลงทุน
**สรุป**
Top-Down Analysis เป็นกลยุทธ์การเทรดที่ทรงพลัง ซึ่งช่วยให้เทรดเดอร์สามารถวิเคราะห์ตลาดอย่างเป็นระบบ มองภาพรวม และจับจังหวะการเทรดได้อย่างแม่นยำ การนำหลักการของ Top-Down Analysis ไปปรับใช้ในการเทรด จะช่วยเพิ่มประสิทธิภาพในการตัดสินใจ และเพิ่มโอกาสในการประสบความสำเร็จในตลาดการเงินได้อย่างยั่งยืน
-

@ fd208ee8:0fd927c1
2025-02-06 15:58:38
## Beginning at the start
In my previous article, [The Establishment](https://next-alexandria.gitcitadel.eu/publication?d=the-gitcitadel-blog-the-establishment-3-by-stella-v-1), I answered the question: "How do we form a company?" I realize, now, that I was getting a bit ahead, of myself, as the precursor to a *company* is a *team*, and many people struggle to form teams. So, I will go back to the beginning, and then you can read both articles to the end, and then stop.
## The Initiation
The first, and most-difficult step of team formation, is *the initiation*. We know that it must be the most-difficult, as it's the step that carries the highest potential reward, and it's the step that is tried-and-failed most often. (Some people, like Elon Musk or Donald Trump, are born Initiators with excellent follow-through, but this archetype is exceedingly thin on the ground because it requires you to be mildly autistic, have barely-throttled ADHD, and/or tend to megalomania, also popularly known as "toxic masculinity", "CEO personality", or "being a successful military officer".)
Someone needs to form a useful, attractive Vision and then motivate other people to help them achieve it. That sounds really easy, but it's actually brutally difficult because
* You have to come up with an idea that is coherent, plausible, and inspiring.
* You have to be able to communicate that idea to other people and make it appealing to them, by tying it into their own personal goals and desires.
* You have to be able to hone and reformulate that idea, constantly, to correct it or to re-motivate the other team members.
* You have to defend the idea against detractors, naysayers, and trolls, and you have to do it so vociferously, that it will erode your own popularity among those who disagree with you and open you to personal attacks.
* You have to be able to focus on the idea, yourself, for a long stretch of time, and not allow yourself to get bored, lazy, or distracted.

So, just do and be all of those things, and then initiate the team, with the method I will name the *Hatbock Method*. It is so named because of the classic, German initiation ritual, in which an Initiator stands up, loudly defines their Vision and calls into a group "Wer hat Bock?" (roughly, "Who has the hunger/desire?") and whoever responds with "Ich hab Bock." (roughly, "Yes, I hunger for this.") is a part of the team.
Then the Initiator says, "Okay, everyone with the hunger, let's sit down together, and discuss this some more." (This "sitting" is literally called a "seating", or "Sitzung", which is the German word for "meeting".)
## The Sitting
We now get to the second most difficult part of team formation: figuring out *where to sit*. Most teams get this wrong, repeatedly, and many teams dissolve or fracture under the difficulty of this momentous decision. You would think organizing yourselves online would make this easier ("Oh, we'll just meet online!"), but the number of places available for sitting online are limitless. You can talk your whole Vision into the ground, with laborous discussions and migrations between Chachi, OxChat, Telegram, SimpleX, Slack, Discord, WhatsApp, GitHub, Teams, Coracle, Matrix... you get the idea.
Try to keep in mind that the Vision is more important than the seating area, and go with the flow. Simply, find someplace and go there. Worry about it again, at a later date. Don't lose momentum. Sit down and start discussing the Vision, *immediately*.

Now, this next bit is very important:
> Do not let anyone outside your team influence where you sit!
...unless they are providing your team with some good, service, or income, that makes choosing their preferred location the superior choice.
This is the German *Stammtisch* principle, where a host encourages you to come sit down, regularly, in some particular place, because your sitting there provides them with some benefit: they can overhear your conversations, get you to test out their seating area, sell you refreshments, etc. Your choice of seating, in other words, is a valuable good, and you should only "sell" it to someone who rewards you in measure. They have to reward you because their preferred seating area wasn't your immediate and obvious choice, so there was probably something unappealing or uncertain about the seating area.
## Plan it in
Once you've sat down, and finished your rough draft of the Vision, you need to figure out *when to sit*. This is the third most-difficult part of team formation. (Yes, don't worry, it gets easier as it goes along.)
The most popular plan is the Wirsehenuns Plan (roughly, "We'll see each other, around.") This can work quite well, if you just want to have a loose collaboration, that calls itself together in an ad hoc fashion, when a team member feels the need. Also known as "@ me, bros".
It's not a great plan for more intensive collaboration, as that tends to need a certain amount of velocity, to actually happen, as the speed of movement has a centrifugal effect on the tasks. Team momentum, in other words, creates a sort of gravity, that keeps the team together as a unit. So, for deeper teamwork, I would recommend the Stammtisch variant: name a place and date/time, when you will next meet. Preferably, on a rotating schedule: daily, weekly, last Thursday of the month, etc.
And then meet there and then. And discuss amongst yourselves. Set clear, short-term tasks (and assign them to particular people!), medium-term strategies, and longer-term goals. *Write everything down.* Anything not written down, is a suggestion, not an assigned task.
If you find your Stammtisch becoming increasingly rewarding and productive, and your goals start moving closer and closer into sight, then you might want to formalize your team structure further, [as a company](https://next-alexandria.gitcitadel.eu/publication?d=the-gitcitadel-blog-the-establishment-3-by-stella-v-1).
-

@ 3eba5ef4:751f23ae
2025-02-13 09:00:41
Security is fundamental to any blockchain. It ensures that all tokens are secure. When talking about a virtual machine and the smart contract platform it forms, security comes in two main aspects:
* The code running on the virtual machine must be secure
* The virtual machine itself should also be designed to facilitate safer code execution
The first aspect often gets sufficient attention. When it comes to [CKB](https://www.nervos.org/), we now encourage developers to write scripts in Rust for maximum security, reserving pure C code only for those who fully understand its risks. Additionally, higher-level languages have been introduced in CKB to strike a better balance between productivity and security.
Virtual machine security was a major focus when CKB-VM was originally designed. Many potential risks were addressed at the architectural level, though some—despite thorough research—were still left open. One such issue is **Return-Oriented Programming (ROP)**—a rather ingenious attack. It exploits executable code that has been legitimately loaded into memory, making widely effective protections (e.g., [W^X](https://yakihonne.com/write-article)) futile. It spans multiple architectures and is constantly evolving. Although we’ve spent a great deal of effort in the early days on ROP, we did not implement specific countermeasures to prevent it. Now, with new RISC-V extensions now available, it is the perfect time to introduce design-level protections against ROP.
## Acknowledgments
Before diving deeper, we would like to acknowledge Todd Mortimer from the OpenBSD team. His work on ROP mitigations at the OpenBSD kernel in 2018-2019 significantly inspired our research and this article. We highly recommend his [talk](https://www.youtube.com/watch?v=ZvSSHtRv5Mg), slide decks from [AsiaBSDCon 2019](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf) and [EuroBSD 2018](https://www.openbsd.org/papers/eurobsdcon2018-rop.pdf), and this [paper](https://www.openbsd.org/papers/asiabsdcon2019-rop-paper.pdf) for a deeper understanding of ROP. Several examples on x64 ROP attacks in this post are also drawn from his research.
## Typical Attack Workflow
While there are many sophisticated [ways](https://www.wired.com/2016/06/clever-attack-uses-sound-computers-fan-steal-data/) of attacks, a common attack on a program typically follows this process:
Prepare a [shellcode](https://en.wikipedia.org/wiki/Shellcode)— a piece of binary code to perform specific actions (e.g., running a shell or other programs on the target computer).
Exploit one possible vulnerability in the target system, most commonly a [buffer overflow](https://en.wikipedia.org/wiki/Buffer_overflow) attack. The attack could be initiated via a network protocol (such as HTTP) against a remote system, or via command line input to a target program;
As the result of the attack, the shellcode is inserted to a designated memory region of the target system and gets executed, allowing the attacker to achieve their goal. The consequences vary, like gaining unauthorized access to sensitive data, destroying certain data/machine, planting malicious programs onto the target for further actions, manipulating control flow.
While traditional systems face a wide range of attacks, blockchains run in their own limited and unique runtime environment, rendering many conventional attacks irrelevant. Major blockchain security threats includes:
* **Private key security**: Blockchain wallets rely on private keys, which are prime targets for various attacks.
* **Smart contract vulnerability**: Poorly written smart contracts contain logic flaws that lead to security risks.
* **Virtual machine security**: Attacker may send malicious inputs to a smart contract, causing it to terminate unexpectedly with a success status—despite lacking proper credentials.
This post focuses specifically on attacks targeting the blockchain’s virtual machine—in our case—CKB Virtual Machine (CKB-VM) specifically.
## CKB’s Early Approach
While it is impossible to predict every attack, disrupting the typical attack workflow is an effective defense strategy. From its inception, CKB-VM has implemented [W^X](https://en.wikipedia.org/wiki/W%5EX) protection: at any given time, any memory location in CKB-VM is either writable (allowing data modification) or executable (allowing data execution)—but never both. Once a memory region is marked as **executable**, it cannot be reverted to **writable** throughout the lifecycle of the current CKB-VM instance. Only writable memory location can be **frozen** to executable.
This design significantly disrupts the typical attack workflow. For shellcode to execute on CKB-VM, it must reside in **executable** memory. However, an attacker can only provide shellcode as part of program inputs, which are loaded into **writable** memory. As long as a CKB script does not voluntarily mark input data as **executable** (a highly unlikely scenario), the shellcode remains inert. Additionally, attempting to overwrite existing **executable** shellcode is also futile, since executable memory region is unwritable, and cannot be converted back to writable.
This way, W^X is a well-established security technique widely used in modern hardwares, operating systems, and virtual machines. Although it cannot prevent all possible attacks, W^X effectively shields many by breaking the standard attack workflow. Even if an attacker successfully injects shellcode into a target machine, the attack is incomplete due to the inability to execute it.
## Understanding ROP
While W^X is effective, it does not solve all our problems. This leads to the topic of this post: **Return-oriented Programming (ROP)**. Instead of explicitly injecting new code, ROP exploits executable code that already resides in the target machine’s memory. Essentially, ROP builds a shellcode by chaining existing code snippets together that were never intended to function as such. It may sound like a fantasy, but as we shall see from the following examples, ROP is a practical and effective attack technique.
To understand ROP, we must first examine modern CPU architecture and memory layout. While assembly instructions vary in representations and lengths, they are put together in memory one after another as a stream of bytes:

*Image [Source](https://www.quora.com/Is-assembly-language-a-source-code-or-object-code)*
As seen in the above example, different assembly instructions come in different lengths. For x86-64 ISA, an instruction can range from 1 to 7 bytes (RISC ISAs such as ARM or RISC-V have more uniform instruction lengths—we will discuss it later). But in memory, instructions are stored sequentially without gaps.
This means that with a stream of bytes alone, we really don’t know what instructions the stream of bytes consist of. In the above example, meaningful assembly instructions emerge only when we start decoding from the `B8` byte. In a different occasion, assuming we know elsewhere that `B8 22 11` bytes at the front are for certain magic flags, the decoding would start from `00` byte, yielding a totally different instruction set.

*Image [Source](https://www.quora.com/Is-assembly-language-a-source-code-or-object-code)*
It is really the combination of a special program counter (`PC`) register from the CPU and the current memory stream, jointly determine the instructions the CPU executes. Depending on each different ISA or hardware, a booting process initializes a CPU’s `PC` register to a pre-defined value, then loads up instructions from this pre-defined address, and initializes everything related to the operating system. When a user launches a new program, the metadata for each program will contain an `entrypoint` address, where OS sets the CPU’s `PC` register to, in order to start executing the program. It is suffice to say that maintaining a proper `PC` value is a critical job to ensure a computer’s proper function. An invalid `PC` value might lead to a CPU malfunction at best, or at worst, leaking sensitive information or granting attackers unauthorized access.
### Forming an ROP Attack Via ROP Gadgets
Let’s look at the following byte instruction stream in a x86-64 CPU:
```
8a 5d c3 movb -61(%rbp), %bl
```
This 3-byte represents a `mov` instruction: it takes the address of `rbp` register, adds an offset of `-61`, then uses the result as a memory address to load 1 byte data, and finally sets the loaded data to `bl` register. However, if we ignore `8a` and only look at `5b c3` here, it actually represents a different instruction set:
```
5d popq %rbp
c3 retq
```
This byte sequence contains two instructions:
* Pop 8-byte value from stack, and use it to set `rbp` register
* Pop 8-byte value from stack, and use it to set `PC` register, so we continue executing from the new location
We've briefly discussed that shellcode only fulfills a certain task required by the attacker. In fact, the most common type of shellcode simply construct a new shell, where the attacker can execute more operations. Such shellcode can be represented in the following C pseudocode to run a new command via the `execve` syscall:
```
execve(“/bin/sh”, NULL, NULL);
```
To execute this on an x86-64 CPU, the following actions are needed for a syscall:
* `rax` register: must contain the syscall number, for `execve`, it is `59`
* `rdi`, `rsi`, `rdx` registers: hold the first 3 arguments to the syscall. In this case, `rdi` holds a pointer to the C string `/bin/sh`; `rsi` and `rdx` must be zero.
* The `syscall` instruction (or typically `int 80h` on x64) shall be executed
A typical shellcode would be a packed assembly sequence directly doing all of the above instructions. In contrast, ROP attack looks for the following sequences:
```
# Those can set the value of different registers from values on the stack
pop %rax; ret
pop %rdi; ret
pop %rsi; ret
pop %rdx; ret
# Finally, trigger the syscall
syscall
```
Each of these small code sequences, are conventionally callled **ROP gadgets**. An attacker searches for these gadgets in the target program or system libraries (such as libc). Once these required gadgets are obtained, the attacker pieces together a sequence of data, much like the following:

With the prepared data sequence, the attacker can exploit a vulnerability in the target computer or program, such as typical buffer overflow attack. During this process, the attacker performs three key actions:
* Pushes (or overwrites existing data) the crafted data sequence to the stack
* Sets the stack pointer (top of the stack) to `X + 64`
* Sets the `PC` register to the address of a code sequence, `pop %rax; ret` in the existing program or libc memory space
Now the attack proceeds step by step as follows:
1. The CPU runs `pop %rax; ret`. With the stack pointer pointing to `X + 64`, the CPU pops `59` from the stack and sets `rax` register to `59`. It then pops the address to code sequence `pop %rdi; ret` from the stack, and sets `PC` to this value;
2. The CPU runs `pop %rdi; ret`. With the stack pointer pointing to `X + 48`, the CPU pops value `X`, pointing to the C string `/bin/sh` from the stack, and sets `rdi` register to `X`. It then pops the address to code sequence `pop %rsi; ret` from the stack, and sets `PC` to this value;
3. The CPU runs `pop %rsi; ret`. With the stack pointer pointing to `X + 32`, the CPU pops `0` from the stack and sets `rsi` register to `0`. It then pops the address to code sequence `pop %rdx; ret` from the stack, and sets `PC` to this value;
4. The CPU runs `pop %rdx; ret`. With the stack pointer pointing to `X + 16`, the CPU pops `0` from the stack and sets `rdx` register to `0`. It then pops the address to code sequence `syscall` from the stack, and sets `P`C to this value;
5. The CPU runs `syscall`. At this point, `rax` holds `59`, `rdi` points to `/bin/sh`, and both `rsi` and `rdx` are zero, the CPU invokes `execve("/bin/sh, NULL, NULL);`, granting the attacker a shell for further manipulations.
This sequence of ROP gadgets, referred to as **ROP chains**, demonstrates how a complete ROP attack works. Two key takeaways are:
* **ROP does not inject new code**. Instead, it injects data into the stack and leverages the existing code loaded in memory and marked them as executable. W^X protections hence cannot prevent ROP attacks.
* **Attackers can mine ROP gadgets from the [libc](https://en.wikipedia.org/wiki/C_standard_library) library**. This is because modern computers employs [protection rings](https://en.wikipedia.org/wiki/Protection_ring) as a way for privilege encapsulations: on x86-64 computers, programs normally run at ring level 3, while libc runs at ring level 1. Lower ring levels have higher privileges, meaning that even if a program misbehaves, its capacities are limited at ring level 3. However, by using ROP gadgets in the libc library which runs at ring level 1, ROP attacks can have higher privileges and execute more damaging operations then normal shellcodes.
Note that the above examples simply show the most basic ROP gadgets. In reality, ROP gadgets come in all kinds of forms. Since they come from compiler outputs, they can be combined in the least expected way, and can vary the forms as new compiler optimizations come out. Numerous tools (e.g., [ropper](https://scoding.de/ropper/), [ropr](https://github.com/Ben-Lichtman/ropr)) and research papers (e.g., *[Experiments on ROP Attack with Various Instruction Set Architectures](https://dl.yumulab.org/papers/42/paper.pdf)*, *[ROPGMN](https://www.sciencedirect.com/science/article/abs/pii/S0167739X24005314)*, *[Detecting and Preventing ROP Attacks using Machine Learning on ARM](https://www.infosun.fim.uni-passau.de/ch/publications/compsac23.pdf)*, *[KROP](https://arxiv.org/pdf/2406.11880)* ) keep coming out, making it almost impossible to enumerate all possible ROP gadget combinations.
### ROP on ARM & RISC-V
ROP attacks are not limited to CISC architectures, where instructions vary in length. They also affect RISC designs, such as [ARM](https://developer.arm.com/documentation/102433/0200/Return-oriented-programming) and [RISC-V](https://pure.royalholloway.ac.uk/ws/portalfiles/portal/37157938/ROP_RISCV.pdf). Take the following sequence for example:
```
13 4f 83 23 0b 00
```
Decoding from the start, the first four bytes represent `xori t5,t1,568` following the RISC-V ISA. But if we skip the first two, the latter four represent `lw t2,0(s6)`. This illustrates that a byte stream interpretation also requires `PC` register in a RISC design such as RISC-V. As a result, one can find ROP gadgets from a RISC-V program as well.
### ROP on CKB-VM
CKB’s RISC-V machine operates in a more restricted environment: for programs running on CKB, there are no `execve` syscalls to hijack a running shell, and all runtime states are publicly visible on a public blockchain like CKB. However, ROP attacks can still occur on CKB: one could construct an ROP chain that sets `a0` to `0`, `a7` to `93`, then executes `ecall`. This causes CKB-VM to immediately return with a success code (`0`), potentially allowing a script to pass validation when it should have failed—such as a lock script succeeding without a valid signature.
### Short Recap
Let’s briefly recap what we’ve learned so far:
* ROP attacks utilize existing executable code for malicious purposes. W^X cannot prevent ROP.
* ROP is possible across multiple architecture, including x86-64, ARM, RISC-V, and CKB.
* The landscape of ROP is constantly evolving. With new tools, techniques, and research emerging regularly, it’s impossible to foresee all ROP gadgets.
ROP has been extensively studied over the years, leading to various mitigation strategies, which can be broadly categorized into two main approaches:
* **Software Solutions**: Covering techniques like rewriting code sequences and implementing Retguard to prevent the creation of ROP gadgets
* **Hardware Solutions**: Introducing additional CPU instructions with Control Flow Integrity (CFI) checks to safeguard control flow.
I’ll explore these strategies in greater detail in the following sections.
## Software Solutions to Mitigate ROP
### Rewriting Sequence
Certain instruction sequences are often targeted to form ROP gadgets. To prevent ROP, one approach is to alter the compiler, so that such sequences can never be generated. Take the following example:
```
89 c3 mov %eax,%ebx
90.
```
In x86-64, `c3` represents the `ret` instruction, making it a potential target for ROP gadgets. We can rewrite it into the following equivalent sequence:
```
48 87 d8 xchgq %rbx, %rax
89 d8 movl %ebx, %eax
48 87 d8 xchgq %rbx, %rax
```
The new sequence lacks `c3` byte at the expense of more bytes and more executed instructions. However, it is really up to real benchmarks to see if this causes noticeable overhead.
Further analysis has revealed that the `rbx` register in x86-64 is often the source of ROP gadgets, due to the way Intel encodes x86-64 instructions. Hence, the OpenBSD team decided to avoid `rbx` register wherever possible, reducing the number of potential ROP gadgets.
Again, this approach comes at the cost of having bigger code fragments, more instructions to execute, and an additional patched compiler. While OpenBSD has integrated these changes into its distribution, other environments must weigh the benefits against the costs.
For a deeper dive, I would strongly recommend Todd Mortimer’s [work](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf).
### Retguard’s Solution: Prologue and Epilogue
Todd Mortimer also introduced Retguard in this [work](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf) for securing OpenBSD known. ROP attacks typically occur when you enter a function `foo`, but the stack was manipulated, so the CPU exits to another code fragment that is not `foo`. What if to verify that, at each function exit, it is the same function for exiting and entering?
Retguard introduces two components to perform this task:
* **Prologue**: A prologue is inserted to each function’s entry, taking two inputs:
- - A `cookie` value, a random data assigned for this particular function.
- - The return address, where to jump to when current function exits—as inputs.
The prologue computes the XOR value of these two, and stores the result into the current function’s [frame](https://en.wikipedia.org/wiki/Call_stack#Stack_and_frame_pointers) section, a dedicated memory region designated to the current function to hold data, separated from the stack.
* **Epilogue**: An epilogue is inserted to the location where a function might exit. It takes two inputs:
- - The saved XOR value from the prologue in the frame section
- - The return address it now can access to (most likely popped from the stack in x64 machine, or read from a special `RA` register in RISC design)
The epilogue computes the XOR of these two. If the result matches the original `cookie`, execution proceeds. Otherwise, the epilogue halts the program, signaling an error.
This prologue-epilogue mechanism in Retguard guards the call stack from tampering. At a noticeable but acceptable cost (both in performance and code size), Retguard eliminates a significant number of ROP gadgets from the OpenBSD kernel. Like other software-based mitigations, it requires a patched compiler, and it is up to each environment to decide if such technique shall be employed.
## Hardware Advancements to Mitigate ROP
In addition to software solutions, hardware-based defenses have also been developed. For instance, Intel has introduced [Indirect Branch Tracking](https://edc.intel.com/content/www/us/en/design/ipla/software-development-platforms/client/platforms/alder-lake-desktop/12th-generation-intel-core-processors-datasheet-volume-1-of-2/007/indirect-branch-tracking/?language=en) feature starting with its 12th generation core processors, using a new instruction `endbr32` or `endbr64` added at every location the program might jump to or call into. When the CPU executes a jump/call, it asserts that the target location is a proper `endbr32` / `endbr64` instruction, before updating the program counter `PC` register to proper values. Otherwise, the CPU halts to terminate the program. This ensures that all control flows will follow the intended way, preventing ROP attacks from redirecting execution arbitrary locations.
Modern OSes have already extensively leveraged `endbr32` / `endbr64` instructions. Ubuntu 24.04, for instance, has included these instructions in its packages:
```
$ objdump -d /bin/bash | head -n 50
/bin/bash: file format elf64-x86-64
Disassembly of section .init:
0000000000030000 <.init>:
30000: f3 0f 1e fa endbr64
30004: 48 83 ec 08 sub $0x8,%rsp
30008: 48 8b 05 d9 7e 12 00 mov 0x127ed9(%rip),%rax # 157ee8 <__gmon_start__@Base>
3000f: 48 85 c0 test %rax,%rax
30012: 74 02 je 30016 <unlink@plt-0xe1a>
30014: ff d0 call *%rax
30016: 48 83 c4 08 add $0x8,%rsp
3001a: c3 ret
Disassembly of section .plt:
0000000000030020 <.plt>:
30020: ff 35 a2 76 12 00 push 0x1276a2(%rip) # 1576c8 <o_options@@Base+0x1cc8>
30026: ff 25 a4 76 12 00 jmp *0x1276a4(%rip) # 1576d0 <o_options@@Base+0x1cd0>
3002c: 0f 1f 40 00 nopl 0x0(%rax)
30030: f3 0f 1e fa endbr64
30034: 68 00 00 00 00 push $0x0
30039: e9 e2 ff ff ff jmp 30020 <unlink@plt-0xe10>
3003e: 66 90 xchg %ax,%ax
30040: f3 0f 1e fa endbr64
30044: 68 01 00 00 00 push $0x1
30049: e9 d2 ff ff ff jmp 30020 <unlink@plt-0xe10>
3004e: 66 90 xchg %ax,%ax
30050: f3 0f 1e fa endbr64
30054: 68 02 00 00 00 push $0x2
30059: e9 c2 ff ff ff jmp 30020 <unlink@plt-0xe10>
3005e: 66 90 xchg %ax,%ax
30060: f3 0f 1e fa endbr64
30064: 68 03 00 00 00 push $0x3
30069: e9 b2 ff ff ff jmp 30020 <unlink@plt-0xe10>
3006e: 66 90 xchg %ax,%ax
30070: f3 0f 1e fa endbr64
30074: 68 04 00 00 00 push $0x4
30079: e9 a2 ff ff ff jmp 30020 <unlink@plt-0xe10>
3007e: 66 90 xchg %ax,%ax
30080: f3 0f 1e fa endbr64
30084: 68 05 00 00 00 push $0x5
30089: e9 92 ff ff ff jmp 30020 <unlink@plt-0xe10>
3008e: 66 90 xchg %ax,%ax
30090: f3 0f 1e fa endbr64
30094: 68 06 00 00 00 push $0x6
30099: e9 82 ff ff ff jmp 30020 <unlink@plt-0xe10>
3009e: 66 90 xchg %ax,%ax
```
The `endbr32` / `endbr64` instructions has been carefully designed, so they are `nop` instructions—meaning they can do nothing at all—on CPUs prior to their introductions. Having them doesn't have any effect on older CPUs but enhances security on supported hardware.
## RISC-V’s Latest Achievements: CFI Extension
The above mitigations against ROP fall into two categories:
* **Compiler Modifications**: Can generate more secure binary assembly code.
* **Additional CPU instructions**: Coming with Control Flow Integrity (CFI) checks to prevent exploitation
Back to the beginning of designing CKB-VM, we throughly studied ROP and recognized that a vulnerability in a CKB script could potentially open the door to ROP attacks. However, we eventually did not introduce any specific mitigation against ROP in CKB-VM. Our decision was to stay aligned with the RISC-V ecosystem, avoiding shipping any custom RISC-V spec with additional instructions that would require a patched compiler. Nor do we want to maintain our own compiler set, eliminating the potential that any RISC-V-compliant compiler shall be able to produce CKB script. As the result, we shipped the first version of CKB-VM without ROP mitigations, but that does not mean we’ve ignore this issue:
* We’ve [reached out](https://groups.google.com/a/groups.riscv.org/g/isa-dev/c/LyZzjJG7_18/m/pCSnKZPdBAAJ) to the RISC-V community for possible extension similar to Intel’s solution, and kept monitoring advancements in this field;
* We’ve been watching over progress and writing secure CKB scripts. Since ROP relies on existing vulnerabilities, secure CKB scripts can kept ROP purely theoretical.
We were thrilled when the **RISC-V CFI (Control-Flow Integrity) Extension** was officialy [ratified](https://github.com/riscv/riscv-cfi/releases/tag/v1.0) in July 2024. Designed by the brilliant minds from the RISC-V Foundation, this extension directly addresses ROP attacks with two key features:
* `Zicfilp` extension introduces **landing pad**: Resembles Intel’s `endbr32` / `endbr64` to ensure that the CPU can only jump to valid, permitted targets.
* `Zicfiss` extension introduces **shadow stack** with a series of instructions:. Offers a hardware solution similar to Retguard, where CPU ensures the control flow integrity or simply puts the call stack, preventing tampering throughout execution.
Together, these features offer the state-of-the-art mitigations against ROP. More importantly, RISC-V CFI is now an official extension, meaning all future RISC-V CPUs, compilers, and tools will support this extension. In fact, LLVM 19 has already [supported](https://releases.llvm.org/19.1.0/docs/ReleaseNotes.html#changes-to-the-risc-v-backend), and I believe other compilers and tools will follow soon.
Once fully adopted, CKB script developers can simply turn them on like a switch during code compilation. Without modifying the code, they can enjoy the security provided by RISC-V CFI extensions. Even if a vulnerability exists in a CKB script, these built-in enforcements can prevent it from being exploited.
## Final Words
Security is complex. While we strive for maximum security, certain design principles might get in the way from introducing specific mitigations. ROP is a prime example: while we did learn much about it early on, implementing the best mitigations needs proper timing. Now the time has come. We are happy to introduce RISC-V CFI in CKB’s next hardfork, bringing stronger security for everyone.
***
✍🏻 Written by Xuejie Xiao
His previous posts include:
* [A Journey Optimizing CKB Smart Contract: Porting Bitcoin as an Example](https://blog.cryptape.com/a-journey-optimizing-ckb-smart-contract)
* [Optimizing C++ Code for CKB-VM: Porting Bitcoin as an Example](https://blog.cryptape.com/optimizing-c-code-for-ckb-vm)
Find more in his personal website [Less is More](https://xuejie.space/).
-

@ 34c964ef:82a60fa4
2025-02-13 08:25:18
The Bond Clean Experts: Your Ultimate Solution for End-of-Lease Cleaning
Moving out of a rental property can be stressful, especially when it comes to meeting the landlord’s cleanliness expectations. That’s where The Bond Clean Experts come in! With professional experience and a commitment to excellence, we ensure your property is spotless, helping you secure your full bond refund without hassle.
Why Choose The Bond Clean Experts?
✅ Experienced Professionals: Our team is trained in industry-standard cleaning techniques to deliver impeccable results.✅ Guaranteed Satisfaction: We offer a bond-back guarantee, ensuring your property meets inspection requirements.✅ Eco-Friendly Products: We use non-toxic, eco-friendly cleaning solutions to protect your health and the environment.✅ Comprehensive Cleaning Services: From kitchens and bathrooms to carpets and windows, we cover every inch of your property.✅ Affordable Pricing: Quality service at competitive rates with no hidden fees.
Our Services Include:
Deep Carpet Cleaning – Removing stubborn stains and odors.
Kitchen & Appliance Cleaning – Ensuring spotless ovens, stovetops, and countertops.
Bathroom Sanitization – Eliminating grime, mold, and bacteria.
Wall & Window Cleaning – Removing marks, dust, and streaks.
Floor & Tile Scrubbing – Bringing back the shine to your flooring.
The Bond Cleaning Process
Inspection & Quote: We assess your property’s cleaning needs and provide a transparent quote.
Thorough Cleaning: Our experts deep clean every area to meet landlord expectations.
Final Touches: We double-check all details and ensure nothing is overlooked.
Satisfaction Guarantee: If needed, we offer a free re-clean to ensure compliance with lease requirements.
Book Your Bond Clean Today!
Don’t risk losing your bond due to subpar cleaning. Let The Bond Clean Experts handle the job with precision and care.
📞 Call us at 0485971499 Serving https://www.bondcleaners.au/bond-cleaning-brisbane/💬 Message us for a free quote!
Make your move-out hassle-free with The Bond Clean Experts! ✨
-

@ f1989a96:bcaaf2c1
2025-02-06 14:01:03
Good morning, readers!
In India, the central bank has taken a significant step toward launching its central bank digital currency (CBDC), the digital rupee. In partnership with fintech firms Mobikwik and Cred, the digital rupee is now available to 180 million users through a new “e₹ wallet,” a CBDC wallet app designed for public use. Predictably, the CBDC comes with tight restrictions, including limits on payment amounts and frequency and extensive personal data collection, raising concerns over financial privacy.
In open-source news, HRF is pleased to announce a collaboration with MIT for the 2025 MIT Bitcoin Expo. This two-day freedom-focused event will explore how Bitcoin and adjacent freedom tech can help combat financial surveillance and repression under authoritarian regimes through expert speakers, panels, workshops, and more. Elsewhere, Joltz became the first self-custodial wallet to support Taproot Assets, enabling access to stable digital dollars on a decentralized network for activists, dissidents, and others in difficult political environments.
We conclude with an extensive guide from Area Bitcoin, a Brazilian education hub, thoroughly examining Brazil’s DREX CBDC and its implications for financial freedom and human rights in Brazil and beyond.
**Now, let’s dive right in!**
### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a)
## **GLOBAL NEWS**
#### **India | Central Bank Partners with Fintech Firms to Pilot Launch CBDC**
The Reserve Bank of India (RBI) [partnered](https://www.businesstoday.in/personal-finance/news/story/mobikwik-cred-join-hands-with-rbi-to-fully-launch-cbdc-ers-for-android-check-features-usage-462318-2025-01-28) with fintech firms MobiKwik and Cred, alongside Yes Bank, to expand the digital rupee, India’s CBDC. With a combined user base of [180 million,](https://www.ledgerinsights.com/fintech-wallets-go-live-in-digital-rupee-cbdc-pilot/) Mobikwik and Cred will act as entry points for public access to the CBDC through their new “e₹ wallet” CBDC app. However, the app mandates video verification and imposes significant restrictions. For instance, a daily transaction cap of ₹50,000 ($577) and ₹10,000 ($115) limit per transaction. The RBI’s decision to embed the digital rupee within existing fintech firms to boost adoption leaves few avenues for financial privacy and freedom as the Indian state [pushes](https://www.lowyinstitute.org/the-interpreter/india-s-plan-world-without-cash) further towards a cashless economy.
#### **El Salvador | Lawmakers Scale Back Bitcoin Legal Tender Law**
El Salvador’s congress [amended](https://www.reuters.com/world/americas/lawmakers-el-salvador-rush-new-bitcoin-reform-after-imf-deal-2025-01-30/) its Bitcoin law, making private sector acceptance of Bitcoin voluntary. The reform follows a $1.4 billion loan agreement with the International Monetary Fund (IMF) that wanted to limit the government’s, citizens’, and economies’ exposure to Bitcoin. Salvadoran lawmaker Elisa Rosales [said](https://www.reuters.com/world/americas/lawmakers-el-salvador-rush-new-bitcoin-reform-after-imf-deal-2025-01-30/) the latest reform guarantees Bitcoin’s “permanence as legal tender” while facilitating its “practical implementation.” But, John Dennehy, founder of the civil society organization [Mi Primer Bitcoin](https://es.myfirstbitcoin.io/), [explained](https://x.com/jdennehy_writes/status/1885346352621617615) that the reform removed “all references of bitcoin as money or legal tender, plus the actual conditions, such as the government accepting bitcoin for things such as taxes, are now prohibited.” The future of freedom technology in El Salvador will be worth monitoring closely as the regime continues to erode protections on civil liberties.
#### **Nigeria | Regime Hikes Telecom Tariffs for Citizens**
In Nigeria, the regime approved a [50% increase](https://thenationonlineng.net/50-tariff-hike-a-necessary-step-or-a-burden-for-nigerians/) in telecom tariffs, further straining citizens already grappling with financial instability. Call rates will rise from 11 to 16.50 naira per minute ($0.0074 to $0.011) and SMS charges from 4 to 6 naira ($0.0026 to $0.004), exacerbating three-decade-high inflation as the ripple effects spread through the economy. Telecom companies justify the price hike as necessary for the sector’s survival amid the naira’s ongoing [devaluation](https://www.bloomberg.com/news/articles/2024-09-13/why-nigeria-s-naira-currency-ngn-usd-slumped-and-why-it-matters). [Deolu Ogunbanjo](https://www.linkedin.com/in/deolu-ogunbanjo-62b5a18b/?originalSubdomain=ng), president of the National Association of Telecoms Subscribers, however, [argues](https://thenationonlineng.net/50-tariff-hike-a-necessary-step-or-a-burden-for-nigerians/) that “this decision shows the government cares more about protecting profits than protecting people.” For Nigerians relying on mobile networks for work, banking, and daily communications, the increased costs will make phone services less accessible, putting even more pressure on civil society under an authoritarian government.
#### **Nicaragua | Inter-American Court of Human Rights Rules Against Ortega**
In Nicaragua, where the financial repression of individuals, opposition, and civil society is widespread, the Inter-American Court of Human Rights [ruled](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) that Daniel Ortega’s reelections since 2011 were illegitimate. This ruling “is the legal confirmation that there is no legitimate president in Nicaragua, but rather a dictator who has usurped power,” [said](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) Jaime Aparicio, a Bolivian lawyer, [adding](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) that “this is the first time that there is a legal precedent determining the illegality of Ortega’s presidency.” In a country where the regime systematically [freezes](https://www.reuters.com/world/americas/nicaragua-govt-accuses-catholic-church-money-laundering-freezes-accounts-2023-05-27/) bank accounts, seizes assets, and [shuts down](https://www.catholicnewsagency.com/news/261539/nicaraguan-dictatorship-shuts-down-more-organizations-including-dominican-nuns) nonprofits to silence dissent, this verdict sets a critical legal precedent against the abuse of state power to secure reelection. While the court lacks enforcement, its ruling strengthens legal challenges to Ortega’s rule and could provide a foundation for future actions against electoral fraud and authoritarian control.
#### **Webinar Series for Nonprofits | Become Unstoppable**
In an era where financial control is weaponized against dissent, the ability to transact freely is more important than ever. For activists and nonprofits operating under oppressive regimes, Bitcoin can offer a way to resist censorship, protect funds, and remain operational.
Join HRF for a free, three-day webinar from March **17–19**, led by Anna Chekhovich, HRF’s Bitcoin nonprofit adoption lead and financial freedom expert at the Anti-Corruption Foundation. The sessions will run daily from **10:30 a.m. to 12:00 p.m. EDT** and are designed specifically to teach human rights defenders and nonprofit organizations how to integrate Bitcoin into their work to challenge state censorship and confiscation in a beginner-friendly way.
### [Register Here](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform)
## BITCOIN AND FREEDOM TECH NEWS
#### **MIT | 2025 Bitcoin Expo**
HRF is partnering with [MIT](https://www.mit.edu/) to host the [2025 MIT Bitcoin Expo](https://mitbtcexpo.org/), a two-day event from April 5-6 at the Stata Center, exploring Bitcoin and freedom technologies as tools for privacy, financial sovereignty, and civil liberties — especially for people living under authoritarian regimes. Now in its 12th year, the expo features keynotes, panels, technical workshops, and hackathons. It brings together developers, activists, students, and researchers to dive into privacy, self-sovereignty, and decentralization. Attendees will also gain hands-on experience and engage in meaningful discussions on the real-world impact of freedom technologies. Learn more about the expo and get your tickets [here](https://mitbtcexpo.org/)**.**
#### **Bitcoin Mining | Two Blocks Mined by Solo Miners This Week**
This week, two solo miners successfully mined Bitcoin blocks, marking a rare and significant event. The first block was [solved](https://x.com/FutureBit/status/1884740065223495821) through a collaborative effort led by the [256 Foundation](https://256foundation.org/) (where 300+ participants [pooled](https://crypto.news/solo-miner-solving-a-block-and-getting-3-146-btc/) their hashrate for a fundraising event). The second block was [mined](https://x.com/SoloSatoshi/status/1885418398345269572) independently through [solo.ckpool](https://solo.ckpool.org/) by a miner using hashrate equivalent to thousands of BitAxe devices, a type of open-source home mining hardware. The news shows that independent miners can still compete outside of large [mining pools](https://river.com/learn/terms/m/mining-pool/). These events reaffirm Bitcoin’s decentralization and censorship resistance, proving that solo mining remains viable with the proper coordination and infrastructure, which is especially key as solo mining can be done privately and quietly under tyrannical regimes.
#### **Joltz Wallet | First Self-Custodial Wallet to Support Taproot Assets**
Joltz has [launched](https://x.com/joltz_btc/status/1885097351108243487) the first self-custodial wallet for [Taproot Assets](https://docs.lightning.engineering/the-lightning-network/taproot-assets), enabling users to hold and transact stablecoins like USDT (Tether) directly on Bitcoin — without intermediaries. Unlike custodial solutions, Joltz ensures users retain full control over their funds while enabling BTC-to-USDT swaps through a user-friendly interface. This could expand access to stable money — particularly for activists and nonprofits in volatile markets in search of digital dollars. However, stablecoins still carry centralization and censorship risks, as issuers like Tether can freeze funds or be beholden to regulatory demands.
#### **Olas | New Updates Enhance Accessibility and Features**
[Olas](https://github.com/pablof7z/olas), an Instagram-like Nostr client built by [Pablof7z](https://github.com/pablof7z), [released](https://github.com/pablof7z/olas/releases/tag/0.2.0) a new update for iOS and Android. The update introduces multiple images per post, Instagram-style filters, and improved video playback. It also enhances its Nostr-native wallet functionality so users can more fluidly receive Bitcoin tips and payments. The client also made Nostr Wallet Connect (NWC), a protocol that allows apps to interact with Bitcoin Lightning wallets, more reliable for end users. Nostr clients like Olas may prove to be a useful tool for censorship-resistant communications on social networks among activists worldwide and stand as a stark contrast to centralized, permissioned alternatives.
#### **OpenSats | Announces Ninth Wave of Bitcoin Grants**
[OpenSats](http://opensats.org), a public nonprofit supporting open-source Bitcoin projects, [announced](https://opensats.org/blog/ninth-wave-of-bitcoin-grants) its ninth wave of Bitcoin grants advancing financial freedom and privacy. Among the recipients, [Nutstash](https://www.nutstash.app/), a multi-platform Cashu ecash wallet, enables private, censorship-resistant Bitcoin transactions — critical for human rights defenders. Another grantee, [El Tor](https://devpost.com/software/el-tor), is developing a fork of the [Tor Network](https://www.torproject.org/) integrated with Bitcoin's Lightning Network, aiming to enhance online privacy for activists and dissidents. HRF welcomes OpenSats’ continued support for decentralized tools in an increasingly surveilled world.
#### **bitcoin++ | Upcoming Bitcoin Developer Conference**
Bitcoin developers and freedom tech enthusiasts will [gather](https://btcplusplus.dev/conf/floripa) in Florianopolis, Brazil, from Feb. 19-22, 2025, for the special “hacking edition” [bitcoin++](https://btcplusplus.dev/) conference. Unlike past bitcoin++ events, which focused on single topics like scripting or ecash, this event will feature hands-on development to enhance Bitcoin’s privacy, scalability, and censorship resistance. Attendees will participate in workshops, live coding challenges, and technical discussions. HRF will help the event include attendees from authoritarian regimes in Latin America. Learn more about the conference or buy tickets [here](https://btcplusplus.dev/conf/floripa).
## RECOMMENDED CONTENT
#### **The Risks of the DREX Central Bank Digital Currency by Area Bitcoin**
In this [article](https://blog.areabitcoin.co/cbdc-drex/), [Area Bitcoin](https://www.areabitcoin.co/), a Brazilian Bitcoin education hub, examines [DREX](https://cbdctracker.hrf.org/currency/brazil), Brazil’s central bank digital currency (CBDC), and its threat to Brazilians’ financial autonomy. DREX operates as a token on a centralized, permissioned blockchain that grants officials sweeping surveillance and control over individual financial activity. Further, its strict Know-Your-Customer (KYC) and Anti-Money Laundering (AML) measures erode financial privacy. Area Bitcoin [warns](https://blog.areabitcoin.co/cbdc-drex/), “By embracing it, we risk surrendering our personal data, the fruits of our labor, and even generational wealth to political and bureaucratic oversight.”
*If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).*
*Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\
*Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)*
*The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*.
[**Subscribe to newsletter**](http://financialfreedomreport.org/)
[**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Visit our website**](https://hrf.org/programs/financial-freedom/)
-

@ 04ed2b8f:75be6756
2025-02-13 08:02:39
Freedom. It’s the word on everyone’s lips, the dream of every soul. We long for it, we chase it, we believe that if we can break free from this chain or that constraint, we will finally be free. **But true freedom is not about external circumstances—it’s about control.**
The truth is, **the most powerful chains are the ones we place on ourselves**. The world can throw its challenges at you, life can dish out its unfair blows, but **if you cannot control yourself, your thoughts, your emotions, your reactions, then you are no different than a prisoner.**
There is no freedom in chaos. There is no freedom in losing control. **Freedom is mastery—mastery of the self.**
## **Freedom Begins Within**
You can have all the money in the world, live in the most luxurious place, and have every material possession your heart desires, but **if you cannot control your impulses, your habits, your desires—none of that will matter.** You are still a slave to your cravings. You are still a puppet to your own emotions, and that is **no real freedom.**
What does freedom look like?
- **It’s the power to act with purpose, not to react out of emotion.**
- **It’s the strength to stay disciplined when every part of you wants to quit.**
- **It’s the courage to say ‘no’ to distractions, to temptation, to things that steer you off course.**
- **It’s the clarity to make choices that serve your growth, not your immediate desires.**
True freedom is the ability to say, “I am in control of myself. I do not let my circumstances control me, nor my emotions rule me. I dictate my actions, my thoughts, my destiny.”
## **Self-Control: The Ultimate Weapon**
The power to control yourself is your greatest weapon. Without it, **you are at the mercy of every challenge, every temptation, and every fleeting emotion**. You may feel like you are “free,” but without self-discipline, you are just a puppet swaying in the wind, vulnerable to every whim that blows your way.
- **The impulse to procrastinate? You overcome it.**
- **The desire to give up? You push through it.**
- **The craving for comfort? You choose growth.**
In the face of any storm, a man with self-control remains grounded, focused, and clear. He doesn’t react in anger or fear—he acts with purpose, with precision, and with vision.
A man who cannot control himself is a man who is owned by his emotions, his desires, his distractions. But the man who conquers his mind, his body, his impulses—he is the one who **owns his life.**
## **The Price of Freedom**
It’s not easy to control yourself. It requires constant effort, relentless discipline, and the courage to face yourself head-on. It means saying ‘no’ to what feels good now, to invest in what will make you stronger later. It means constantly improving, constantly fighting the urge to quit, to give in, to indulge in comfort.
But the price of freedom is worth it. **For when you have control over yourself, no one can take your power.** You become the master of your fate. **You become unshakable.**
## **Freedom Through Discipline**
So, ask yourself: **Are you truly free, or are you simply a slave to your impulses?**
- **Do you control your actions, or do your actions control you?**
- **Are you the master of your emotions, or are they the masters of you?**
Freedom isn’t just about having no chains; it’s about not letting anything control you—least of all yourself. **And when you control yourself, there’s nothing you can’t accomplish.**
A man who cannot control himself is never truly free. But a man who conquers his mind, his habits, his emotions—he is unstoppable.
**Now go and choose to control yourself, and unlock the freedom that’s waiting for you. Or remain a prisoner to your impulses, forever shackled by the chains of your own making. The choice is yours.**
-

@ bf47c19e:c3d2573b
2025-02-13 07:56:50
Originalni tekst na [dvadesetjedan.com](https://dvadesetjedan.com/blog/niko-ne-moze-zabraniti-bitcoin)
###### Autor: [Parker Lewis](https://x.com/parkeralewis) / Prevod na srpski: [Plumsky](https://t.me/Plumski)
---
Ideja da država može nekako zabraniti bitcoin je jedna od poslednjih faza tuge, tačno pred prihvatanje realnosti. Posledica ove rečenice je priznanje da bitcoin “funkcioniše”. U stvari, ona predstavlja činjenicu da bitcoin funkcioniše toliko dobro da on preti postojećim državnim monopolima nad novcem i da će zbog toga države da ga unište kroz regulativne prepreke da bi eliminisale tu pretnju. Gledajte na tvrdnju da će države zabraniti bitcoin kao kondicionalnu logiku. Da li bitcoin funkcioniše kao novac? Ako je odgovor „ne“, onda države nemaju šta da zabrane. Ako je odgovor „da“, onda će države da probaju da ga zabrane. Znači, glavna poenta ovog razmišljanja je pretpostavka da bitcoin funkcioiniše kao novac. Onda je sledeće logično pitanje da li intervencija od strane države može uspešno da uništi upravo taj funkcionalan bitcoin.
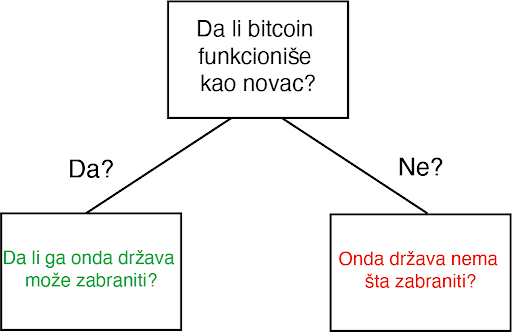
Za početak, svako ko pokušava da razume kako, zašto, ili da li bitcoin funkcioniše mora da proceni ta pitanja potpuno nezavisno od prouzrekovanja državne regulacije ili intervencije. Iako je nesumnjivo da bitcoin mora da postoji uzgred državnih regulativa, zamislite na momenat da države ne postoje. Sam od sebe, da li bi bitcoin funkcionisao kao novac, kad bi se prepustio slobodnom tržištu? Ovo pitanje se širi u dodatna pitanja i ubrzo se pretvara u bunar bez dna. Šta je novac? Šta su svojstva koja čine jednu vrstu novca bolje od druge? Da li bitcoin poseduje ta svojstva? Da li je bitcoin bolja verzija novca po takvim osobinama? Ako je finalni zaključak da bitcoin ne funkcioniše kao novac, implikacije državne intervencije su nebitne. Ali, ako je bitcoin funkcionalan kao novac, ta pitanja onda postaju bitna u ovoj debati, i svako ko o tome razmišlja bi morao imati taj početnički kontekst da bi mogao proceniti da li je uopšte moguće zabraniti. Po svom dizajnu, bitcoin postoji van države. Ali bitcoin nije samo van kontrole države, on u stvari funkcioniše bez bilo kakve saradnje centralizovanih identiteta. On je globalan i decentralizovan. Svako može pristupiti bitcoinu bez potrebe saglasnosti bilo koga i što se više širi sve je teže cenzurisati celokupnu mrežu. Arhitektura bitcoina je namerno izmišljena da bude otporna na bilo koje pokušaje države da ga zabrane. Ovo ne znači da države širom sveta neće pokušavati da ga regulišu, oporezuju ili čak da potpuno zabrane njegovo korišćenje. Naravno da će biti puno bitki i otpora protiv usvajanja bitcoina među građanima. Federal Reserve i Američki Treasury (i njihovi globalni suparnici) se neće ležeći predati dok bitcoin sve više i više ugrožava njihove monopole prihvatljivog novca. Doduše, pre nego što se odbaci ideja da države mogu potpuno zabraniti bitcoin, mora se prvo razumeti posledice tog stava i njegovog glasnika.
#### Progresija poricanja i stepeni tuge
Pripovesti skeptičara se neprestano menjaju kroz vreme. Prvi stepen tuge: bitcoin nikad ne može funkcionisati-njegova vrednost je osnovana ni na čemu. On je moderna verzija tulip manije. Sa svakim ciklusom uzbuđenja, vrednost bitcoina skače i onda vrlo brzo se vraća na dole. Često nazvano kao kraj njegove vrednosti, bitcoin svaki put odbija da umre i njegova vrednost pronađe nivo koji je uvek viši od prethodnih ciklusa globalne usvajanja. Tulip pripovetka postaje stara i dosadna i skeptičari pređu na više nijansirane teme, i time menjaju bazu debate. Drugi stepen tuge predstoji: bitcoin je manjkav kao novac. On je previše volatilan da bi bio valuta, ili je suviše spor da bi se koristio kao sistem plaćanja, ili se ne može proširiti dovoljno da zadovolji sve promete plaćanja na svetu, ili troši isuviše struje. Taj niz kritike ide sve dalje i dalje. Ovaj drugi stepen je progresija poricanja i dosta je udaljen od ideje da je bitcoin ništa više od bukvalno bezvrednog ničega.
Uprkos tim pretpostavnim manjcima, vrednost bitcoin mreže nastavje da raste vremenom. Svaki put, ona ne umire, nasuprot, ona postaje sve veća i jača. Dok se skeptičari bave ukazivanjem na manjke, bitcoin ne prestaje. Rast u vrednosti je prouzrokovan jednostavnom dinamikom tržišta: postoji više kupca nego prodavca. To je sve i to je razlog rasta u adopciji. Sve više i više ljudi shvata zašto postoji fundamentalna potražnja za bitcoinom i zašto/kako on funkcioniše. To je razlog njegovog dugotrajnog rasta. Dokle god ga sve više ljudi koristi za čuvanje vrednosti, neće pasti cena snabdevanja. Zauvek će postojati samo 21 milion bitcoina. Nebitno je koliko ljudi zahtevaju bitcoin, njegova cela količina je uvek ista i neelastična. Dok skeptičari nastavljaju sa svojom starom pričom, mase ljudi nastavljaju da eliminišu zabludu i zahtevaju bitcoin zbog njegovih prednosti u smislu novčanih svojstva. Između ostalog, ne postoji grupa ljudi koja je više upoznata sa svim argumentima protiv bitcoina od samih bitcoinera.

Očajanje počinje da se stvara i onda se debata još jedanput pomera. Sada nije više činjenica je vrednost bitcoina osnovana ni na čemu niti da ima manjke kao valuta; sada se debata centrira na regulaciji državnih autoriteta. U ovom zadnjem stepenu tuge, bitcoin se predstavlja kao u stvari isuviše uspešnom alatkom i zbog toga države ne smeju dozvoliti da on postoji. Zaista? Znači da je genijalnost čoveka ponovo ostvarila funkcionalan novac u tehnološko superiornoj formi, čije su posledice zaista neshvatljive, i da će države upravo taj izum nekako zabraniti. Primetite da tom izjavom skeptičari praktično priznaju svoj poraz. Ovo su poslednji pokušaji u seriji promašenih argumenata. Skeptičari u isto vreme prihvataju da postoji fundamentalna potražnja za bitcoinom a onda se premeštaju na neosnovan stav da ga države mogu zabraniti.
Ajde da se poigramo i tim pitanjem. Kada bih zapravo razvijene države nastupile na scenu i pokušale da zabrane bitcoin? Trenutno, Federal Reserve i Treasury ne smatraju bitcoin kao ozbiljnu pretnju superiornosti dolara. Po njihovom celokupnom mišljenju, bitcoin je slatka mala igračka i ne može da funkcioniše kao novac. Sadašnja kompletna kupovna moć bitcoina je manja od $200 milijardi. Sa druge strane, zlato ima celokupnu vrednost od $8 triliona (40X veću od bitcoina) i količina odštampanog novca (M2) je otprilike 15 triliona (75X veličine bitcoinove vrednosti). Kada će Federal Reserve i Treasury da počne da smatra bitcoin kao ozbiljnu pretnju? Kad bitcoin poraste na $1, $2 ili $3 triliona? Možete i sami da izaberete nivo, ali implikacija je da će bitcoin biti mnogo vredniji, i posedovaće ga sve više ljudi širom sveta, pre nego što će ga državne vlasti shvatiti kao obiljnog protivnika.
Predsednik Tramp & Treasury Sekretar Mnučin o Bitcoinu (2019):
> „Ja neću pričati o bitcoinu za 10 godina, u to možete biti sigurni {…} Ja bi se kladio da čak za 5 ili 6 godina neću više pričati o bitcoinu kao sekretar Trusury-a. Imaću preča posla {…} Mogu vam obećati da ja lično neću biti pun bitcoina.“ – Sekretar Treasury-a Stiv Mnučin
> „Ja nisam ljubitelj bitcoina {…}, koji nije novac i čija vrednost je jako volatilna i osnovana na praznom vazduhu.“ – Predsednik Donald J. Tramp
Znači, logika skeptika ide ovako: bitcoin ne funkcioniše, ali ako funkcioniše, onda će ga država zabraniti. Ali, države slobodnog sveta neće pokušati da ga zabrane dokle god se on ne pokaže kao ozbiljna pretnja. U tom trenutku, bitcoin će biti vredniji i sigurno teži da se zabrani, pošto će ga više ljudi posedovati na mnogo širem geografskom prostoru. Ignorišite fundamentalne činjenice i asimetriju koja je urođena u globalnom dešavanju monetizacije zato što u slučaju da ste u pravu, države će taj proces zabraniti. Na kojoj strani tog argumenta bi radije stajao racionalan ekonomski učesnik? Posedovanje finansijske imovine kojoj vrednost toliko raste da preti globalnoj rezervnoj valuti, ili nasuprot – nemati tu imovinu? Sa pretpostavkom da individualci razumeju zašto je mogućnost (a sve više i verovatnoća) ove realnosti, koji stav je logičniji u ovom scenariju? Asimetrija dve strane ovog argumenta sama od sebe zahteva da je prvi stav onaj istinit i da fundamentalno razumevanje potražnje bitcoina samo još više ojačava to mišljenje.
#### Niko ne moze zabraniti bitcoin
Razmislite šta bitcoin u stvari predstavlja pa onda šta bi predstavljala njegova zabrana. Bitcoin je konverzija subjektivne vrednosti, stvorena i razmenjena u realnošću, u digitalne potpise. Jednostavno rečeno, to je konverzija ljudskog vremena u novac. Kad neko zahteva bitcoin, oni u isto vreme ne zahtevaju neki drugi posed, nek to bio dolar, kuća, auto ili hrana itd. Bitcoin predstavlja novčanu štednju koja sa sobom žrtvuje druge imovine i servise. Zabrana bitcoina bi bio napad na najosnovnije ljudske slobode koje je on upravo stvoren da brani. Zamislite reakciju svih onih koji su prihvatili bitcoin: „Bilo je zabavno, alatka za koju su svi eksperti tvrdili da neće nikad funkcionisati, sada toliko dobro radi i sad ti isti eksperti i autoriteti kažu da mi to nemožemo koristiti. Svi idite kući, predstava je gotova.“verovanje da će svi ljudi koji su učestvovali u bitcoin usvajanju, suverenitetu koji nudi i finansiskoj slobodi, odjednom samo da se predaju osnovnom rušenju njihovih prava je potpuno iracionalna pozicija.
> Novac je jedan od najbitnijih instrumenata za slobodu koji je ikad izmišljen. Novac je to što u postojećem društvu ostvaruje mogućnosti siromašnom čoveku – čiji je domet veći nego onaj koji je bio dostižan bogatim ljudima pre ne toliko puno generacija.“ – F. A. Hajek
Države nisu uspele da zabrane konzumiranje alkohola, droga, kupovinu vatrenog oružja, pa ni posedovanje zlata. Država može samo pomalo da uspori pristup ili da deklariše posedovanje ilegalnim, ali ne može da uništi nešto što veliki broj raznovrsnih ljudi smatra vrednim. Kada je SAD zabranila privatno posedovanje zlata 1933., zlato nije palo u vrednosti ili nestalo sa finansijskog tržišta. Ono je u stvari poraslo u vrednosti u poređenju sa dolarom, i samo trideset godina kasnije, zabrana je bila ukinuta. Ne samo da bitcoin nudi veću vrednosno obećanje od bilo kog drugog dobra koje su države pokušale da zabrane (uključujući i zlato); nego po svojim osobinama, njega je mnogo teže zabraniti. Bitcoin je globalan i decentralizovan. On ne poštuje granice i osiguran je mnoštvom nodova i kriptografskim potpisima. Sam postupak zabrane bi zahtevao da se u isto vreme zaustavi „open source“ softver koji emituje i izvršava slanje i potvrđivanje digitalno enkriptovanih ključeva i potpisa. Ta zabrana bi morala biti koordinisana između velikog broja zemalja, sa tim da je nemoguće znati gde se ti nodovi i softver nalazi ili da se zaustavi instaliranje novih nodova u drugim pravnim nadležnostima. Da ne pominjemo i ustavske pitanja, bilo bi tehnički neizvodljivo da se takva zabrana primeni na bilo kakav značajan način.
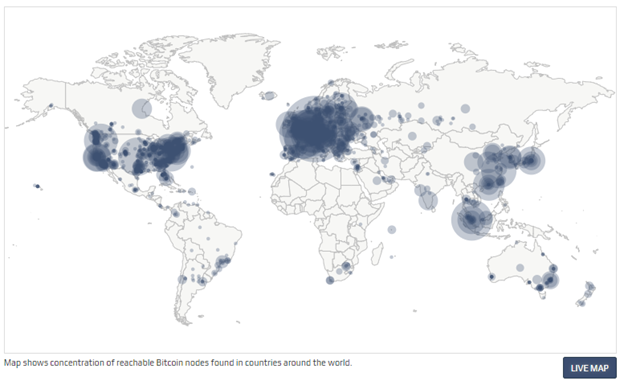
Čak kada bih sve zemlje iz G-20 grupe koordinisale takvu zabranu u isto vreme, to ne bi uništilo bitcoin. U stvari, to bi bilo samoubistvo za fiat novčani sistem. To bi još više prikazalo masama da je bitcoin u stvari novac koji treba shvatiti ozbiljno, i to bi samo od sebe započelo globalnu igru vatanje mačke za rep. Bitcoin nema centralnu tačku za napad; bitcoin rudari, nodovi i digitalni potpisi su rasejani po celom svetu. Svaki aspekt bitcoina je decentralizovan, zato su glavni stubovi njegove arhitekture da učesnici uvek treba kontrolisati svoje potpise i upravljati svojim nodom. Što više digitalnih potpisa i nodova koji postoje, to je više bitcoin decentralizovan, i to je više odbranjiva njegova mreža od strane neprijatelja. Što je više zemalja gde rudari izvršavaju svoj posao, to je manji rizik da jedan nadležni identitet može uticati na njegov bezbednosni sistem. Koordinisan internacionalni napad na bitcoin bi samo koristio da bitcoin još više ojača svoj imuni sistem. Na kraju krajeva, to bi ubrzalo seobu iz tradicionalnog finansijskog sistema (i njegovih valuta) a i inovaciju koja postoji u bitcoin ekosistemu. Sa svakom bivšom pretnjom, bitcoin je maštovito pronalazio način da ih neutrališe pa i koordinisan napad od strane država ne bi bio ništa drugačiji.
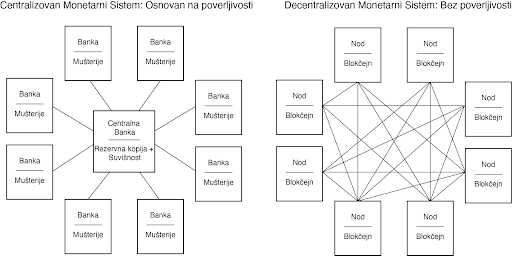
Inovacija u ovoj oblasti koja se odlikuje svojom „permissionless“ (bez dozvole centralnih identiteta) osobinom, omogućava odbranu od svakojakih napada. Sve varijante napada koje su bile predvidjene je upravo to što zahteva konstantnu inovaciju bitcoina. To je ona Adam Smitova nevidljiva ruka, ali dopingovana. Pojedinačni učesnici mogu da veruju da su motivisani nekim većim uzrokom, ali u stvari, korisnost kaja je ugrađena u bitcoin stvara kod učesnika dovoljno snažan podsticaj da omogući svoje preživljavanje. Sopstveni interes milione, ako ne milijarde, nekoordinisanih ljudi koji se jedino slažu u svojom međusobnom potrebom za funkcionalnim novcem podstiče inovacije u bitcoinu. Danas, možda to izgleda kao neka kul nova tehnologija ili neki dobar investment u finansijskom portfoliju, ali čak i ako to mnogi ne razumeju, bitcoin je apsolutna nužnost u svetu. To je tako zato što je novac nužnost a historijski priznate valute se fundamentalno raspadaju. Pre dva meseca, tržište američkih državnih obveznica je doživeo kolaps na šta je Federal Reserve reagovao time što je povećao celokupnu količinu dolara u postojanju za $250 milijardi, a još više u bliskoj budućnosti. Tačno ovo je razlog zašto je bitcoin nužnost a ne samo luksuzni dodatak. Kada inovacija omogućava bazično funkcionisanje ekonomije ne postoji ni jedna država na svetu koja može da zaustavi njenu adopciju i rast. Novac je nužnost a bitcoin znatno poboljšava sistem novca koji je ikada postojao pre njega.
Sa više praktične strane, pokušaj zabranjivanja bitcoina ili njegove velike regulacije od nadležnosti bi direktno bilo u korist susedne nadležnih organa. Podsticaj da se odustane od koordinisanog napada na bitcoin bi bio isuviše veliki da bi takvi dogovori bili uspešni. Kada bi SAD deklarisovale posed bitcoina ilegalnim sutra, da li bi to zaustavilo njegov rast, razvoj i adopciji i da li bi to smanjilo vrednost celokupne mreže? Verovatno. Da li bi to uništilo bitcoin? Ne bi. Bitcoin predstavlja najpokretljivije kapitalno sredstvo na svetu. Zemlje i nadležne strukture koje kreiraju regulativnu strukturu koja najmanje ustručava korišćenje bitcoina će biti dobitnici velike količine uliva kapitala u svoje države.
#### Zabrana Bitcoinove Zatvoreničke Dileme
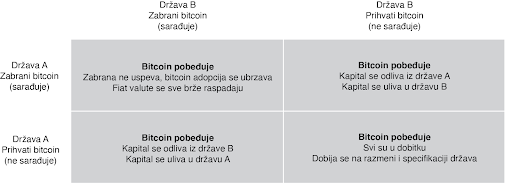
U praksi, zatvorenička dilema nije igra jedan na jedan. Ona je multidimenzijska i uključuje mnoštvo nadležnosti, čiji se interesi nadmeću međusobno, i to uskraćuje mogućnosti bilo kakve mogućnosti zabrane. Ljudski kapital, fizički kapital i novčani kapital će sav ići u pravcu država i nadležnosti koje najmanje ustručuju bitcoin. To se možda neće desiti sve odjednom, ali pokušaji zabrane su isto za badava koliko bi bilo odseći sebi nos u inat svom licu. To ne znači da države to neće pokušati. India je već probala da zabrani bitcoin. Kina je uvela puno restrikcija. Drugi će da prate njihove tragove. Ali svaki put kada država preduzme takve korake, to ima nepredvidljive efekte povećanja bitcoin adopcije. Pokušaji zabranjivanja bitcoina su jako efektivne marketing kampanje. Bitcoin postoji kao sistem nevezan za jednu suverenu državu i kao novac je otporan na cenzuru. On je dizajniran da postoji van državne kontrole. Pokušaji da se taj koncept zabrani samo još više daje njemu razlog i logiku za postojanje.
#### Jedini Pobednički Potez je da se Uključiš u Igru
Zabrana bitcoina je trošenje vremena. Neki će to pokušati; ali svi će biti neuspešni. Sami ti pokušaji će još više ubrzati njegovu adopciju i širenje. Biće to vetar od 100 km/h koji raspaljuje vatru. To će ojačati bitcoin sve više i doprineće njegovoj pouzdanosti. U svakom slučaju, verovanje da će države zabraniti bitcoin u momentu kada on postane dovoljno velika pretnja rezervnim valutam sveta, je iracionalan razlog da se on no poseduje kao instrument štednje novca. To ne samo da podrazumeva da je bitcoin novac, ali u isto vreme i ignoriše glavne razloge zašto je to tako: on je decentralizovan i otporan na cenzure. Zamislite da razumete jednu od nojvećih tajni današnjice i da u isto vreme tu tajnu asimetrije koju bitcoin nudi ne primenjujete u svoju korist zbog straha od države. Pre će biti, neko ko razume zašto bitcoin funkcioniše i da ga država ne može zaustaviti, ili nepuno znanje postoji u razumevanju kako bitcoin uopšte funckioniše. Počnite sa razmatranjem fundamentalnih pitanja, a onda primenite to kao temelj da bi procenili bilo koji potencijalan rizik od strane budućih regulacija ili restrikcija državnih organa. I nikad nemojte da zaboravite na vrednost asimetrije između dve strane ovde prezentiranih argumenata. Jedini pobednički potez je da se uključite u igru.
Stavovi ovde prezentirani su samo moji i ne predstavljaju Unchained Capital ili moje kolege. Zahvaljujem se Fil Gajgeru za razmatranje teksta i primedbe.
[Originalni tekst](https://unchained.com/blog/bitcoin-cannot-be-banned/)
-

@ ec42c765:328c0600
2025-02-05 22:53:03
てすと
nostr:nevent1qqst3uqlls4yr9vys4dza2sgjle3ly37trck7jgdmtr23uuz52usjrqqqnjgr
nostr:nevent1qqsdvchy5d27zt3z05rr3q6vvmzgslslxwu0p4dfkvxwhmvxldn9djguvagp2
test
-

@ 8d5ba92c:c6c3ecd5
2025-02-05 22:06:18
**There I was, minding my own business at the airport (i.e., arranging the list of Bitcoin/Freedom podcasts for the next seven hours of flight), when I came across a scene that could have been ripped straight from a show about the decline of civilization. Heart-wrenching. Shocking. Dystopian. To put it simply, what the f*ck?!**
## Prologue.
A family of five, including two early-school kids (let’s call them 'Timmy' and 'Amy', around 5 and 7 years old), a father who looked like he’d given up on life, and a perfect mother multitasking like a pro—breastfeeding a baby while chowing down on a Big Mac.
Oh yeah, the whole family was happily consuming their McDonald’s junk as if it was their daily ritual.
Watching little kids eat that stuff? A mix of anger and sadness. But seeing a breastfeeding mother give her newborn absolute garbage? The scene I can’t forget.
She also washed it all down with some fizzy, sugary, chemical-laden sludge later on. Still, while breastfeeding. Because, you know, nothing screams nourishment like a steady diet of artificial stuff. Best to get them hooked in the first few months, right?
## Act One: The Mother’s Masterpiece.
A modern-day Madonna, cradling her infant while balancing junk food’s finest. The baby, blissfully unaware of the nutritional betrayal unfolding in real-time, probably wasn’t even dreaming of normal food that might one day help it grow into a healthy being.
Seeing this scene, knowing all the options available at the airport—many much more reasonable than this crap—and watching the family enjoy their 'sacred food', I’m almost certain this little one had been getting a side of heavily processed rubbish long before it even left the womb...
Rave: A standing ovation for conscious parenting.
## Act Two: Innocent Contribution.
Just when I thought the scene couldn’t get worse, little “Timmy” decided to play bartender. With the enthusiasm of a child clearly raised on a steady diet of Big Macs and Coca-Cola (or whatever other delicacies were on offer), he extended his cup to his tiny brother or sister. The devoted mother, of course, helped him guide the straw to the baby’s mouth. *“Drink, little one! Drink not just from my body, but directly from the cup. Drink this (crap) with us!”*
Why not? If McDonald’s was good enough for everyone in the family, surely it was good enough for the baby sibling, right?
They all looked almost proud of Timmy’s little “sharing is caring” moment. Meanwhile, my heart shattered into a million pieces, each one screaming, *“Seriously?! Should I interfere? How would they react?”*
I was close enough to keep taking photos, staring at them with my mouth probably hanging open, horror written all over my face. The mother met my gaze once—cold, unreadable. No 'leave us alone.' No 'it’s our business.' No 'what's wrong, tell us.' Just... nothing.
My husband, noticing my growing frustration and sensing I was about to step in, whispered, *“Let it go. You won’t save them in 10 minutes at the airport.”*
Maybe he was right. But I’ll be thinking about it for a long time…
## Act Three: A Recipe for Regret.
It was as if the parents had collectively agreed that their bodies were nothing more than human garbage bins, and their children were just smaller versions of the same.
Let’s be clear: adults can do whatever they want with their health. If you want to treat your body like a landfill, go ahead—it’s your funeral (literally). But when you drag your kids into it, it’s no longer a personal choice. It’s more like a crime. These children didn’t sign up for a life of artificial flavors, empty calories, and a future riddled with health problems. They deserve better.
And if you’re reading this thinking, *‘What’s the big deal?’*—let's talk.
My brain is on the verge of exploding, trying to understand how anyone could actively contribute to the slow, painful destruction of the people they (presumably) love. You should love and respect your own body, and even more so the lives of your kids. What could possibly justify feeding your family McDonald's if it’s not the very last option you have on earth to survive? Please, help me understand why!
## Epilogue: The Aftertaste.
As I stepped into the boarding line, I couldn’t shake the thought: Is this really where we are now?
A world where care and nutritional awareness no longer exist. Where junk food became a family tradition. Where children are raised on a cocktail of chemicals when better options are right there!
**To the McDonald’s family at the airport—and anyone on their way to becoming one:
Not sure if you enjoyed your meal. If you did, I wish you luck. You’ll need it.**
https://i.nostr.build/e8f3h9iuDNQbtmaF.png
**And please, maybe—just maybe—consider giving your kids a chance. They deserve more than a trash life packed with chemicals in a paper bag.**
----
BTC Your Mind. Let it ₿eat.
Şelale
-

@ 91bea5cd:1df4451c
2025-02-04 17:15:57
### Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits
Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C.
e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
#### Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid()
RETURNS TEXT
AS $$
DECLARE
-- Crockford's Base32
encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000';
output TEXT = '';
unix_time BIGINT;
ulid BYTEA;
BEGIN
-- 6 timestamp bytes
unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT;
timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER);
timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes
ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output;
END
$$
LANGUAGE plpgsql
VOLATILE;
```
#### ULID TO UUID
```sql
CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$
DECLARE
-- 16byte
bytes bytea = E'\\x00000000 00000000 00000000 00000000';
v char[];
-- Allow for O(1) lookup of index values
dec integer[] = ARRAY[
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 255, 255, 255,
255, 255, 255, 255, 255, 255, 255, 0, 1, 2,
3, 4, 5, 6, 7, 8, 9, 255, 255, 255,
255, 255, 255, 255, 10, 11, 12, 13, 14, 15,
16, 17, 1, 18, 19, 1, 20, 21, 0, 22,
23, 24, 25, 26, 255, 27, 28, 29, 30, 31,
255, 255, 255, 255, 255, 255, 10, 11, 12, 13,
14, 15, 16, 17, 1, 18, 19, 1, 20, 21,
0, 22, 23, 24, 25, 26, 255, 27, 28, 29,
30, 31
];
BEGIN
IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN
RAISE EXCEPTION 'Invalid ULID: %', ulid;
END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits)
bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]);
bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2));
bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4));
bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1));
bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3));
bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits);
bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2));
bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4));
bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1));
bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3));
bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]);
bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2));
bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4));
bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1));
bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3));
bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$
BEGIN
RETURN encode(parse_ulid(ulid), 'hex')::uuid;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
```
#### UUID to ULID
```sql
CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$
DECLARE
encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
output text = '';
uuid_bytes bytea = uuid_send(id);
BEGIN
-- Encode the timestamp
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4)));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2));
output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5)));
output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output;
END
$$
LANGUAGE plpgsql
IMMUTABLE;
```
#### Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql
-- Cria a extensão pgcrypto para gerar uuid
CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID
CREATE OR REPLACE FUNCTION gen_lrandom()
RETURNS TEXT AS $$
DECLARE
ts_millis BIGINT;
ts_chars TEXT;
random_bytes BYTEA;
random_chars TEXT;
base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ';
i INT;
BEGIN
-- Pega o timestamp em milissegundos
ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32
ts_chars := '';
FOR i IN REVERSE 0..11 LOOP
ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1);
END LOOP;
-- Gera 10 bytes aleatórios e converte para base32
random_bytes := gen_random_bytes(10);
random_chars := '';
FOR i IN 0..9 LOOP
random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1);
IF i < 9 THEN
random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1);
ELSE
random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1);
END IF;
END LOOP;
-- Concatena o timestamp e os caracteres aleatórios
RETURN ts_chars || random_chars;
END;
$$ LANGUAGE plpgsql;
```
#### Exemplo de USO
```sql
-- Criação da extensão caso não exista
CREATE EXTENSION
IF
NOT EXISTS pgcrypto;
-- Criação da tabela pessoas
CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela
SELECT
*
FROM
"pessoas"
WHERE
uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F';
```
### Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-

@ da0b9bc3:4e30a4a9
2025-02-13 06:36:12
Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/884478
-

@ fd208ee8:0fd927c1
2025-02-02 10:33:19
# GitCitadel Development Operations
We, at GitCitadel, have been updating, moving, and rearranging our servers, for quite some time. As a rather large, complex, sprawling project, we have the infrastructure setup to match, so we've decided to give you all a quick run-down of what we are doing behind-the-scenes.
## Supplier Coordination
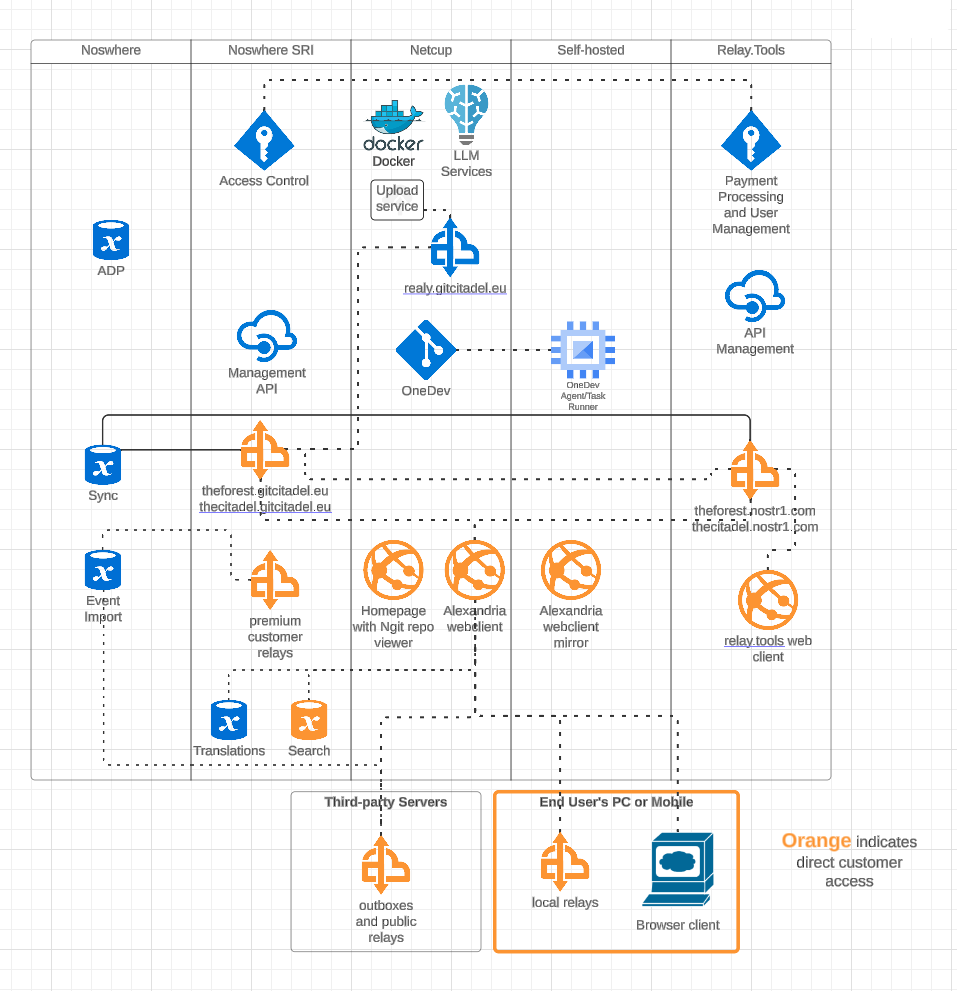
Our first task, this week, was figuring out who would host what where. We have four different locations, where our infra is stored and managed, including two locations from our suppliers. We got that straightened out, quickly, and it's all slowly coming together and being connected and networked. Exciting to watch our DevOps landscape evolve and all of the knowledge-transfer that the interactions provide.
## OneDev Implementation
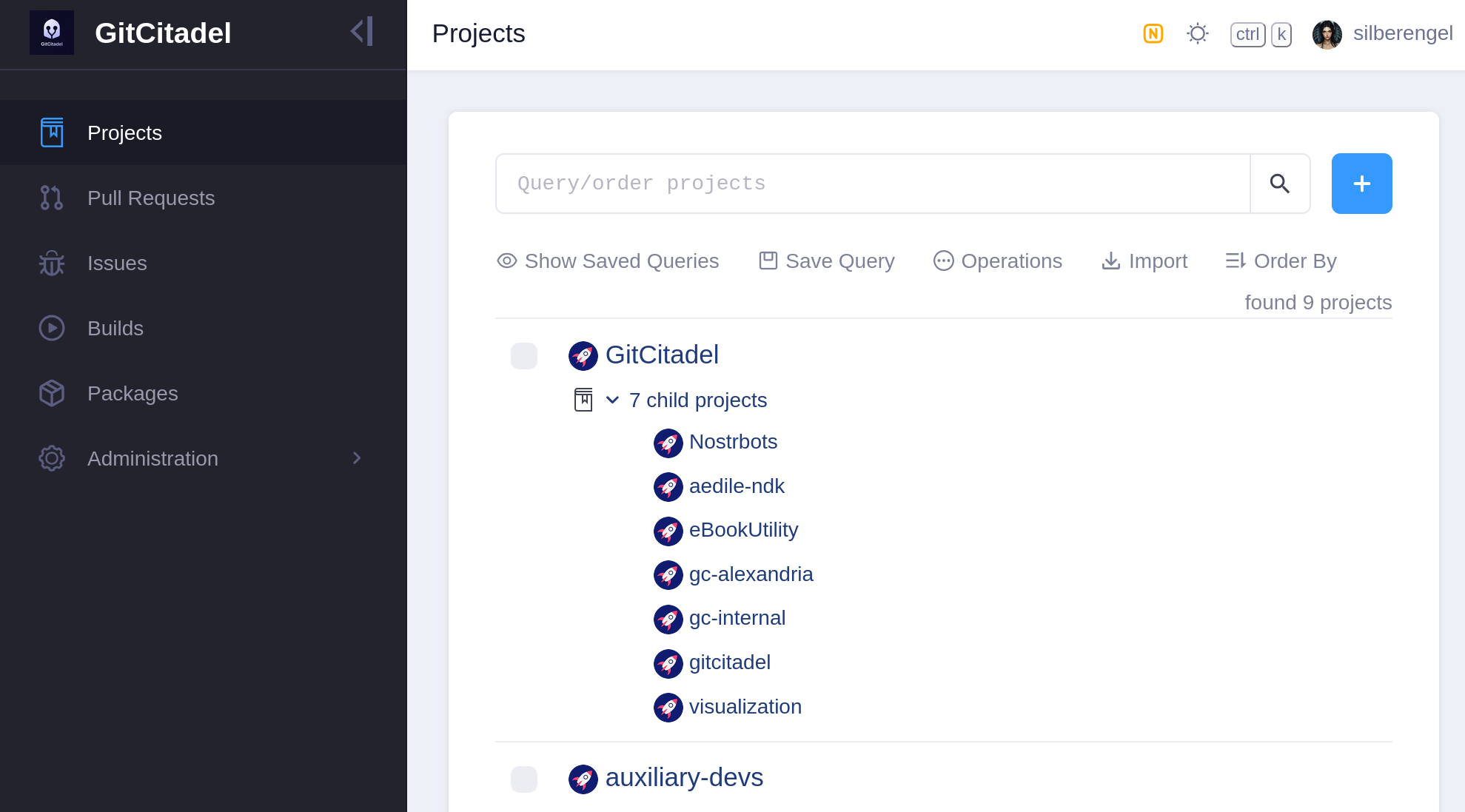
Our biggest internal infra project this week was the migration of all of our issues from Jira, build scripts from Jenkins, and repos from GitHub to a [self-hosted OneDev instance](https://onedev.gitcitadel.eu). In the future, all of our internal build, test, issue, patch/PR, etc. effort will take place there. We also have a separate repo there for communicating with external developers and suppliers.
Our [team's GitHub projects](https://github.com/ShadowySupercode) will be demoted to mirrors and a place for external devs to PR to. Public issues and patches will continue to be managed over our self-hosted [GitWorkshop instance](nostr:naddr1qvzqqqrhnypzplfq3m5v3u5r0q9f255fdeyz8nyac6lagssx8zy4wugxjs8ajf7pqy88wumn8ghj7mn0wvhxcmmv9uqq5emfw33kjarpv3jkcs83wav).
We're especially glad to finally escape the GitHub Gulag, and avoid being bled dry by Jira fees, without having to give up the important features that we've come to know and love. So, yay!
## Next Infrasteps
### Automated Testing
Now, that we have everything tied up in one, neat, backed-up package, we can finally move on to the nitty-gritty and the dirty work. So, we're rolling up our sleeves and writing the Selenium smoke test for our [Alexandria client](https://next-alexandria.gitcitadel.eu). We'll be running that in Docker containers containing different "typical Nostr" images, such as Chrome browser with Nostr Connect signing extension, or Firefox browser with Nos2x-fox extension. Once we get the Nsec Bunker and Amber logins going, we'll add test cases and images for them, as well. (Yes, we can do Bunker. I hope you are in awe at our powers).
We are also designing an automated infrastructure test, that will simply rattle through all the various internal and external websites and relays, to make sure that everything is still online and responsive.
After that, a Gherkin-based [Behave feature test](https://behave.readthedocs.io/en/latest/) for Alexandria is planned, so that we can prevent regression of completed functionality, from one release to the next.
The Gherkin scenarios are written and attached to our stories before development begins (we use acceptance tests as requirements), a manual test-execution is then completed, in order to set the story to *Done*. These completed scenarios will be automated, following each release, with the resulting script linked to from the origin story.
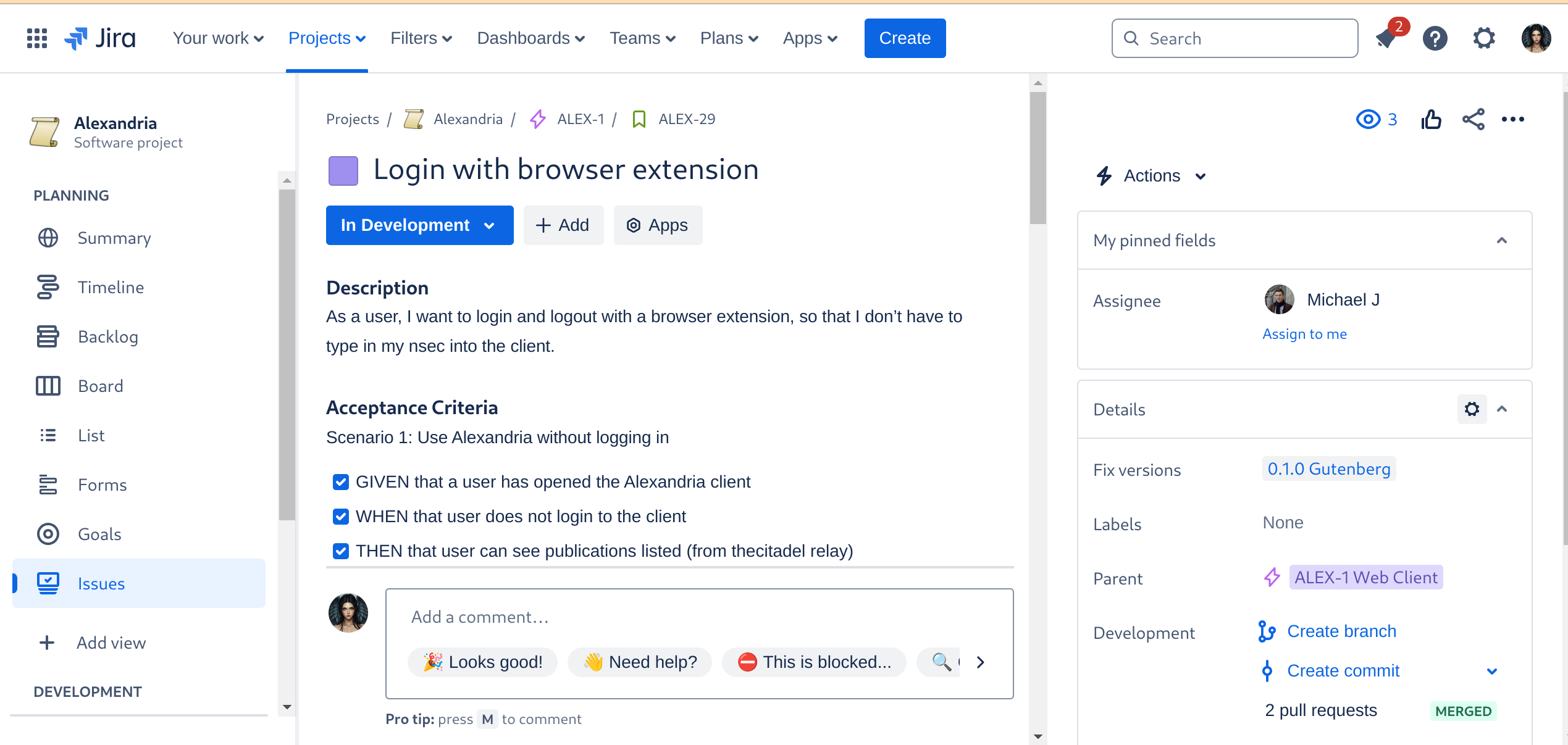
### Automated Builds
As the crowning glory of every DevOps tool chain stands the build automation. This is where everything gets tied together, straightened out, configured, tested, measured, and -- if everything passes the quality gates -- released. I don't have to tell you how much time developers spend staring at the build process display, praying that it all goes through and they can celebrate a Green Wave.
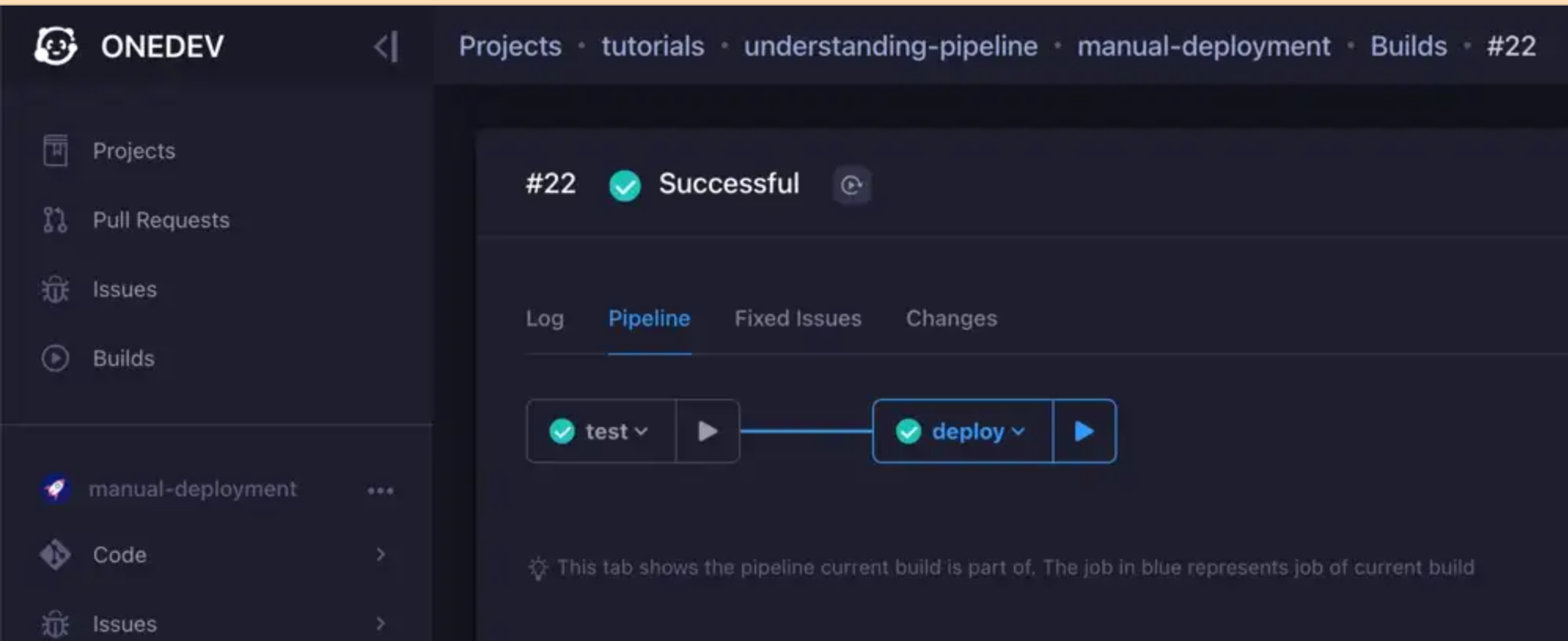
We are currently designing the various builds, but the ones we have defined for the Alexandria client will be a continuous delivery pipeline, like so:
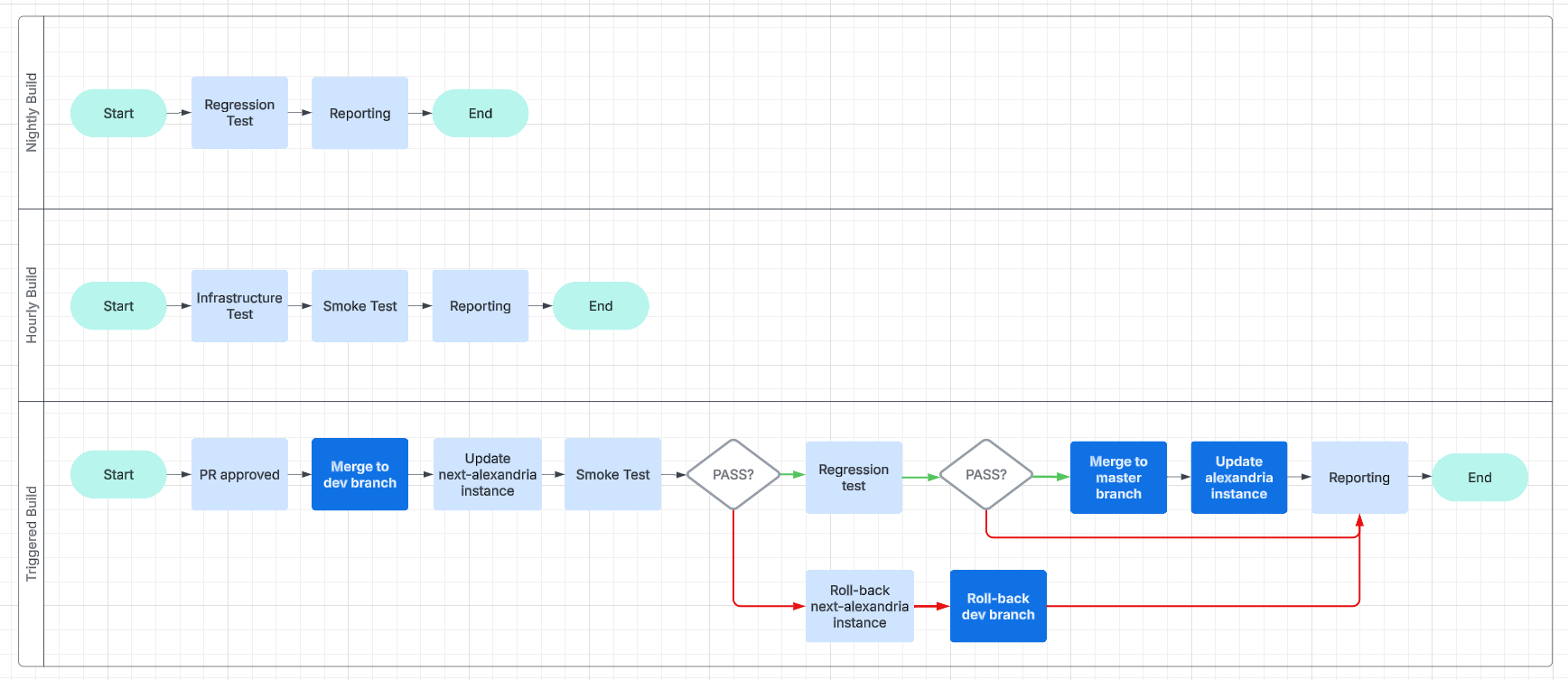
This will make it easier for us to work and collaborate asynchronously and without unnecessary delays.
### Expanding the Status Page
And, finally, we get to the point of all of this busyness: reporting.
We are going to have beautiful reports, and we are going to post them online, on our [status page](https://status.gitcitadel.com). We will use bots, to inform Nostriches of the current status of our systems, so go ahead and follow our [GitCitadel DevOps npub](nostr:npub16p0fdr2xccfs07hykx92t0cascac69xjuwaq38kjqy3aawt5hx8s82feyj), to make sure you don't miss out on the IT action.
## Building on stone
All in all, we're really happy with the way things are humming along, now, and the steady increase in our productivity, as all the foundational work we've put in starts to pay off. It's getting easier and easier to add new team members, repos, or features/fixes, so we should be able to scale up and out from here. Our GitCitadel is built on a firm foundation.
Happy building!
-

@ 9e69e420:d12360c2
2025-02-01 11:16:04

Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-

@ d360efec:14907b5f
2025-02-13 05:54:17

**ภาพรวม LUNCUSDT (OKX):**
LUNCUSDT กำลังอยู่ในช่วงที่ *มีความผันผวนสูงและมีความไม่แน่นอนมาก* แม้ว่าในอดีต (TF Day) จะเคยมีสัญญาณของการพยายามกลับตัวเป็นขาขึ้น (Breakout EMA 50 และเกิด Golden Cross) แต่ปัจจุบันแรงซื้อเหล่านั้นเริ่มอ่อนแรงลง และมีแรงขายเข้ามาในตลาดมากขึ้น ทำให้เกิดความขัดแย้งระหว่าง Timeframes ต่างๆ

**สถานะปัจจุบัน:**
* **แนวโน้ม:**
* **TF Day:** เริ่มไม่แน่นอน (จากเดิมที่เป็น Early Uptrend) - แม้ว่าราคาจะยังอยู่เหนือ EMA 50/200 แต่ Money Flow เริ่มแสดงสัญญาณเตือน
* **TF4H:** เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50) - Money Flow บ่งบอกถึงแรงขายที่เข้ามา
* **TF15:** ผันผวนสูง, ไม่มีทิศทางชัดเจน (Sideways) - Money Flow แสดงถึงแรงขาย แต่ก็มีแรงซื้อกลับเข้ามาบ้าง
* **Money Flow (LuxAlgo):**
* **TF Day:** แรงซื้อเริ่มอ่อนแรงลงอย่างมีนัยสำคัญ, มีแรงขายเข้ามา
* **TF4H:** แรงขายมีมากกว่าแรงซื้อ
* **TF15:** แรงขายและแรงซื้อผสมกัน, โดยรวมแรงขายยังมากกว่า
* **EMA:**
* **TF Day:** EMA 50/200 เป็นแนวรับ/แนวต้าน
* **TF4H:** EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวต้าน
* **TF15:** EMA 50/200 เป็นแนวต้าน
**โครงสร้างราคา (SMC):**
| Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) |
| :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- |
| Day | ด้านบนและล่าง | ด้านบน | เริ่มก่อตัว (แต่ไม่แข็งแกร่ง) | - |
| 4H | ด้านบน | ด้านบน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | มี EQH หลายจุด |
| 15m | ด้านบนและล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | มี EQH และ EQL หลายจุด |
**แนวรับ-แนวต้านสำคัญ:**
| Timeframe | แนวรับ | แนวต้าน |
| :-------- | :----------------------------------------------------------- | :--------------------------------------------------------------------- |
| Day | EMA 50 (≈0.00010000), EMA 200 (≈0.00008000), 0.00006000-0.00007000 | 0.00017953 (High ล่าสุด), 0.00014000 (Volume Profile) |
| 4H | EMA 50 (≈0.00007000), 0.00006000-0.00007000 | EMA 200 (≈0.00008000), 0.00008132, บริเวณ 0.00010000-0.00012000 (EQH) |
| 15m | บริเวณ Low ล่าสุด | EMA 50, EMA 200, บริเวณ 0.000075-0.000076 (EQH) |
**กลยุทธ์ (LUNCUSDT):**
1. **Wait & See (ทางเลือกที่ดีที่สุด):**
* **เหตุผล:** ความขัดแย้งระหว่าง Timeframes สูงมาก, แนวโน้มไม่ชัดเจน, Money Flow ใน TF4H และ TF15 เป็นลบ
* รอให้ราคาแสดงทิศทางที่ชัดเจนกว่านี้ (ยืนเหนือ EMA 50 ใน TF4H ได้, Breakout แนวต้านใน TF15)
2. **Buy on Dip (Day, 4H) - *ความเสี่ยงสูงมาก ไม่แนะนำ*:**
* **เหตุผล:** แนวโน้มระยะยาวอาจจะยังเป็นขาขึ้นได้ (ถ้าไม่หลุดแนวรับสำคัญ)
* **เงื่อนไข:** *ต้อง* รอสัญญาณการกลับตัวใน TF15 ก่อน
* **จุดเข้า:** พิจารณาเฉพาะบริเวณแนวรับที่แข็งแกร่งมากๆ (EMA ของ Day/4H) *และต้องดู TF15 ประกอบ*
* **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15
3. **Short (15, ความเสี่ยงสูงมาก):**
* **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ
* **เงื่อนไข:** ราคาไม่สามารถ Breakout EMA หรือแนวต้านอื่นๆ ใน TF15 ได้
* **จุดเข้า:** บริเวณ EMA หรือแนวต้านของ TF15
* **Stop Loss:** เหนือ High ล่าสุดของ TF15
**คำแนะนำ (เน้นย้ำ):**
* **LUNC เป็นเหรียญที่มีความเสี่ยงสูงมาก (High Risk):** มีความผันผวนสูง และอาจมีการเปลี่ยนแปลงอย่างรวดเร็ว
* **ความขัดแย้งของ Timeframes:** สถานการณ์ของ LUNCUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง
* **Money Flow:** บ่งบอกถึงแรงขายที่เริ่มเข้ามา และแนวโน้มขาขึ้น (ระยะกลาง-ยาว) ที่อ่อนแอลง
* **ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด:** "รอ" เป็นกลยุทธ์ที่ดีที่สุด
* **Risk Management:** สำคัญที่สุด ไม่ว่าจะเลือกกลยุทธ์ใด ต้องมีการบริหารความเสี่ยงที่ดี
**สรุป:** LUNCUSDT กำลังอยู่ในช่วงเวลาที่ยากลำบากและมีความเสี่ยงสูงมากที่สุดในบรรดา 3 เหรียญที่เราวิเคราะห์กันมา การตัดสินใจที่ผิดพลาดอาจนำไปสู่การขาดทุนได้ ควรพิจารณาอย่างรอบคอบก่อนเข้าเทรดทุกครั้ง และ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดสำหรับนักลงทุนส่วนใหญ่ค่ะ
**Disclaimer:** การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-

@ d360efec:14907b5f
2025-02-13 05:27:39

**ภาพรวม XRPUSDT (OKX):**
XRPUSDT กำลังอยู่ในช่วงสำคัญ แนวโน้มระยะยาว (TF Day) เริ่มมีสัญญาณบวกของการเป็นขาขึ้น (Early Uptrend) หลังราคา Breakout EMA 50 และ Money Flow สนับสนุน อย่างไรก็ตาม แนวโน้มระยะกลาง (TF4H) เริ่มแสดงความอ่อนแอลง โดยราคาพักตัวลงมาทดสอบแนวรับสำคัญ และ Money Flow บ่งชี้ถึงแรงซื้อที่ลดลงและแรงขายที่เพิ่มขึ้น ส่วนแนวโน้มระยะสั้นมาก (TF15) เป็นขาลงชัดเจน

**แนวโน้ม:**
* **TF Day:** เริ่มเป็นขาขึ้น (Early Uptrend) - Breakout EMA 50, Money Flow เป็นบวก
* **TF4H:** เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50 และ EQL) - Money Flow เริ่มเป็นลบ
* **TF15:** ขาลง (Downtrend) ระยะสั้นมาก - ราคาหลุด EMA, โครงสร้างราคาเป็น Lower Highs/Lows, Money Flow เป็นลบ
**โครงสร้างราคา (SMC):**
| Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) |
| :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- |
| Day | ด้านบน (Breakout EMA 50) | ไม่ชัดเจน | เริ่มก่อตัว (แต่ยังไม่ชัดเจน) | - |
| 4H | ด้านบน | ไม่ชัดเจน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | EQH: 3.00-3.20, EQL: 2.2667 |
| 15m | ด้านล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | EQH: 2.48-2.50, EQL: 2.38 |

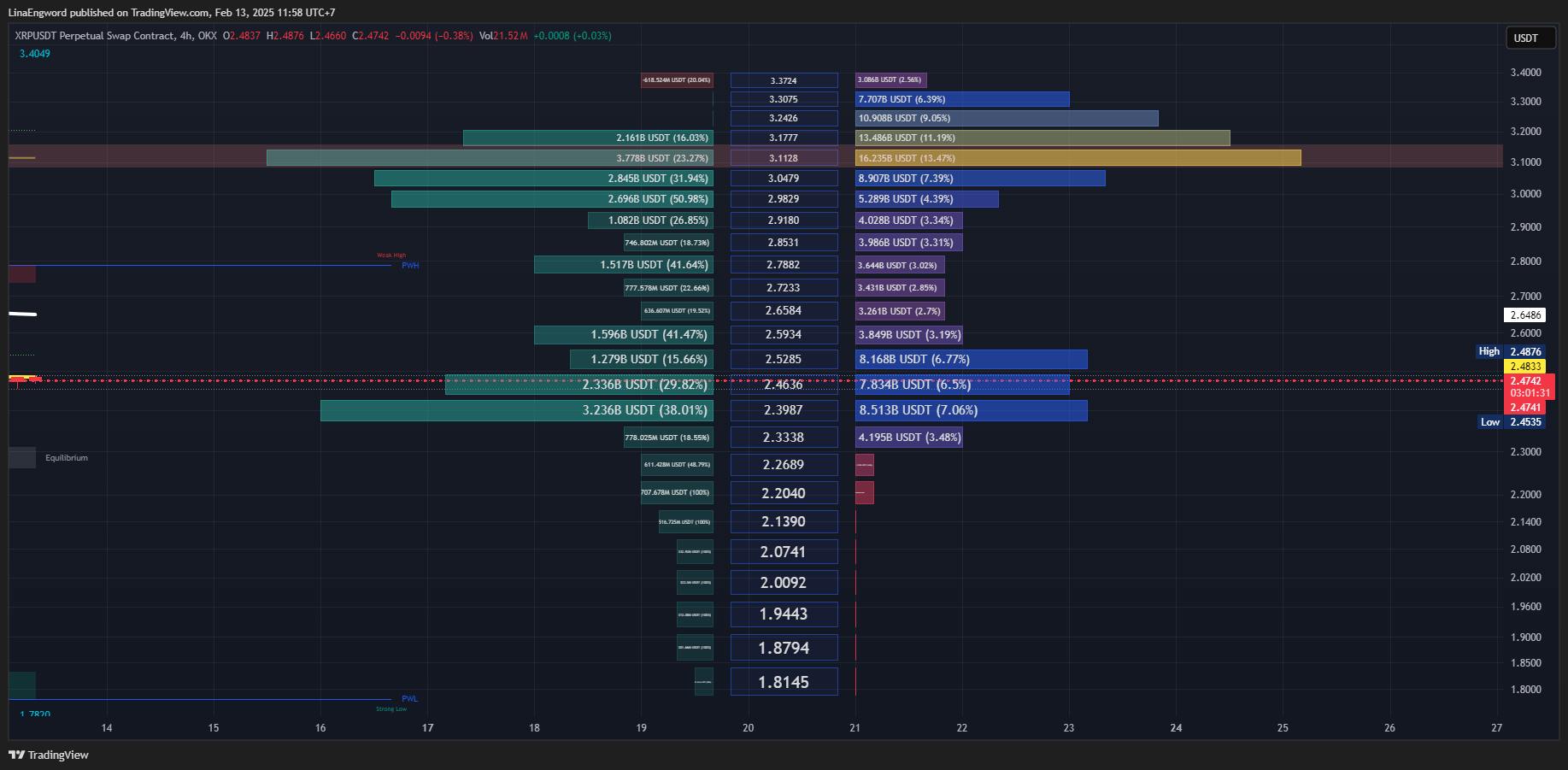
**Money Flow (LuxAlgo):**
* **TF Day:** แรงซื้อแข็งแกร่ง
* **TF4H:** แรงซื้อเริ่มอ่อนแรงลง, แรงขายเริ่มเข้ามา
* **TF15:** แรงขายมีอิทธิพลเหนือกว่า
**EMA (Exponential Moving Average):**
* **TF Day:** EMA 50 & 200 เป็นแนวรับ
* **TF4H:** EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวรับถัดไป
* **TF15:** EMA 50 & 200 เป็นแนวต้าน
**แนวรับ-แนวต้านสำคัญ:**
| Timeframe | แนวรับ | แนวต้าน |
| :-------- | :----------------------------------------------------- | :----------------------------------------------------------------------- |
| Day | EMA 50 (≈1.56), EMA 200 (≈1.08) | 3.4049 (High), 3.00-3.20 (EQH) |
| 4H | EMA 50 (≈2.20), *2.2667 (EQL)*, EMA 200, 1.7820 | 3.4049, 2.3987 (Volume Profile), 3.00-3.20 (EQH) |
| 15m | 2.38 (EQL, Volume Profile), 2.3274 | EMA 50, EMA 200, 2.4196, Equilibrium (≈2.44), 2.48-2.50 (EQH) |
**กลยุทธ์ (XRPUSDT):**
1. **Wait & See (ทางเลือกที่ดีที่สุด):**
* **เหตุผล:** ความขัดแย้งระหว่าง Timeframes สูง, TF4H กำลังทดสอบแนวรับสำคัญ, Money Flow ใน TF4H และ TF15 เป็นลบ
* รอให้ราคาแสดงทิศทางที่ชัดเจน (ยืนเหนือ EMA 50 ใน TF4H ได้ หรือ Breakout แนวต้านใน TF15)
2. **Buy on Dip (Day, 4H) - *ความเสี่ยงสูงมาก*:**
* **เหตุผล:** แนวโน้มระยะยาวยังมีโอกาสเป็นขาขึ้น, Money Flow ใน TF Day เป็นบวก
* **เงื่อนไข (สำคัญมาก):** *ต้อง* รอสัญญาณการกลับตัวใน TF15 ก่อน เช่น:
* Breakout แนวต้านย่อยๆ พร้อม Volume
* Money Flow (TF15) เปลี่ยนเป็นสีเขียว
* Bullish Candlestick Patterns
* **จุดเข้า (Day):** EMA 50, EMA 200 (*ดู TF15 ประกอบ*)
* **จุดเข้า (4H):** EMA 50, *2.2667 (EQL)* (*ดู TF15 ประกอบ*)
* **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ
3. **Short (15, ความเสี่ยงสูงมาก):**
* **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ
* **เงื่อนไข:** ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้
* **จุดเข้า:** บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ
* **Stop Loss:** เหนือ High ล่าสุดของ TF15
**คำแนะนำ:**
* **ความขัดแย้งของ Timeframes:** XRPUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง
* **Money Flow:** Day เป็นบวก, 4H เริ่มเป็นลบ, 15m เป็นลบ
* **EMA 50 (TF4H) & EQL 2.2667:** จุดชี้ชะตา
* **ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด:** "รอ" ดีที่สุด
* **Risk Management:** สำคัญที่สุด
**สรุป:** สถานการณ์ของ XRPUSDT ตอนนี้มีความเสี่ยงสูงมาก และไม่เหมาะกับนักลงทุนที่รับความเสี่ยงได้ต่ำ การ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดค่ะ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-

@ bf6e4fe1:46d21f26
2025-01-31 01:51:03
{"title":"test","content":"test"}
-

@ d360efec:14907b5f
2025-02-13 04:47:20

**ภาพรวม BTCUSDT :**
Bitcoin (BTCUSDT) กำลังอยู่ในช่วงสำคัญ แม้ว่าแนวโน้มหลักในระยะกลางถึงยาว (TF Day & 4H) จะยังคงเป็นขาขึ้นที่แข็งแกร่ง แต่ในระยะสั้นมาก (TF15) กลับแสดงสัญญาณของความอ่อนแอและการปรับฐานลงมา ทำให้เกิดความไม่แน่นอนในทิศทางของราคา อย่างไรก็ตาม *Money Flow ใน TF Day บ่งชี้ว่าแรงซื้อโดยรวมยังคงแข็งแกร่ง*

**แนวโน้ม:**
* **TF Day:** ขาขึ้น (Uptrend) แข็งแกร่ง – ราคาอยู่เหนือ EMA 50 และ EMA 200, โครงสร้างราคาเป็น Higher Highs (HH) และ Higher Lows (HL), *Money Flow เป็นบวก (แรงซื้อ)*
* **TF4H:** ขาขึ้น (Uptrend) – ราคาอยู่เหนือ EMA, มีการพักตัวลงมา (Pullback) แต่ยังไม่เสียโครงสร้างขาขึ้น, *Money Flow เริ่มอ่อนแรง (แรงซื้อลดลง, แรงขายเพิ่มขึ้น)*
* **TF15:** ขาลง (Downtrend) ระยะสั้นมาก – ราคาหลุด EMA และแนวรับย่อย, โครงสร้างราคาเป็น Lower Highs (LH) และ Lower Lows (LL), *Money Flow เป็นลบ (แรงขาย)*
**โครงสร้างราคา (SMC):**
* **TF Day:** ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS)
* **TF4H:** ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS), มี Equal Highs (EQH) ที่เป็นแนวต้าน
* **TF15:** บ่งบอกถึงแนวโน้มขาลงระยะสั้น (BOS ด้านล่าง, LH, LL), มี EQH เป็นแนวต้าน
**Money Flow (LuxAlgo) - สรุป:**
* **TF Day:** แรงซื้อยังคงแข็งแกร่งอย่างชัดเจน
* **TF4H:** แรงซื้อเริ่มอ่อนแรงลง, มีแรงขายเข้ามา
* **TF15:** แรงขายมีอิทธิพลเหนือกว่า

**EMA (Exponential Moving Average):**
* **TF Day & 4H:** EMA 50 & 200 เป็นแนวรับสำคัญ
* **TF15:** EMA 50 & 200 กลายเป็นแนวต้าน
**แนวรับ-แนวต้านสำคัญ:**
| Timeframe | แนวรับ | แนวต้าน |
| :-------- | :------------------------------------------------------------------------- | :-------------------------------------------------------------- |
| Day | EMA 50, EMA 200, 96,000-98,000, 85,724.7 | 109,998.9 (High เดิม) |
| 4H | EMA 50, EMA 200, 96,000-98,000, 89,037.0 | 109,998.9 (EQH, High เดิม) |
| 15m | 95,200 (Low ล่าสุด), 94,707.4 (Low ก่อนหน้า) | EMA 50, EMA 200, บริเวณ 96,000, 96,807.8, 97,000-97,200 |
**กลยุทธ์ (BTCUSDT):**
1. **Buy on Dip (Day, 4H) - *มีความน่าเชื่อถือมากขึ้น แต่ยังคงต้องระมัดระวัง*:**
* **เหตุผล:** แนวโน้มหลักยังเป็นขาขึ้น, Money Flow ใน TF Day แข็งแกร่ง
* **เงื่อนไข:** *ยังคงต้องรอสัญญาณการกลับตัวของราคาใน TF15 ก่อน* (Breakout แนวต้านย่อย, Money Flow TF15 เป็นบวก, Bullish Candlestick Patterns)
* **จุดเข้า (Day):** EMA 50, EMA 200, บริเวณ 96,000-98,000
* **จุดเข้า (4H):** EMA 50
* **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ
2. **Short (15, ความเสี่ยงสูงมาก):**
* **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow TF15 เป็นลบ
* **เงื่อนไข:** ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้
* **จุดเข้า:** บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ
* **Stop Loss:** เหนือ High ล่าสุดของ TF15
3. **Wait & See (ทางเลือกที่ปลอดภัย):**
* **เหตุผล:** ความขัดแย้งระหว่าง Timeframes ยังคงมีอยู่
* รอให้ตลาดเฉลยทิศทางที่ชัดเจนกว่านี้
**คำแนะนำ (เน้นย้ำ):**
* **Money Flow ใน TF Day:** เป็นปัจจัยบวกที่สำคัญ ทำให้กลยุทธ์ Buy on Dip มีน้ำหนักมากขึ้น
* **ความขัดแย้งของ Timeframes:** ยังคงต้องระวัง TF15 ที่เป็นขาลง
* **Volume:** การ Breakout/Breakdown ใดๆ ควรมี Volume สนับสนุน
* **Risk Management:** สำคัญที่สุด
**สรุป:**
สถานการณ์ของ BTCUSDT โดยรวมยังคงเป็นบวก (ขาขึ้น) แต่มีความเสี่ยงในระยะสั้นจาก TF15 การตัดสินใจลงทุนควรพิจารณาจาก Timeframe ที่เหมาะสมกับสไตล์การเทรดของคุณ และอย่าลืมบริหารความเสี่ยงเสมอค่ะ
**Disclaimer:** การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-

@ cc8d072e:a6a026cb
2025-01-30 17:20:24
Recently, I had the opportunity to work as an advisor for an AI agent project, which is created by team with a lot of fin-tech software develop experience. As we coded together, their real-time questions and challenges provided unique insights into the hurdles software engineers face when transitioning to AI development. They would pause at moments that most AI engineers take for granted - "How can we be sure the agent understood correctly?", "What if the model makes a mistake?", "How do we handle the uncertainty?" These weren't just isolated questions; they represented the fundamental paradigm shift required when moving from traditional software engineering to AI development. And thats why i think it might be worthy to take sometime write down this article and if you are going to start your first AI agent programming, spending 5 min reading t his will save you a lot of time later.
### 1. Shifting from Deterministic to Probabilistic Thinking
- Traditional software engineering deals with deterministic outcomes
- AI systems operate on probability rather than certainty
- Engineers need to adapt from "100% correct" mindset to accepting probabilistic outcomes
- Blockchain developers may find this particularly challenging due to their background in exact, deterministic systems
### 2. Understanding Core AI Concepts
(There are a lot of concepts to understand, but i will focus on the most frequently asked ones)
#### Memory Management
- **Short-term Memory**: Implemented through conversation context
- **Long-term Memory**: Implemented through vector databases (RAG - Retrieval Augmented Generation)
- Context length management is crucial due to LLM token limitations
#### Language Models and Fine-tuning
- Base models (like GPT) provide general intelligence
- Domain-specific knowledge can be added through:
- Fine-tuning with custom datasets
- Adding RAG layers for specific knowledge domains
### 3. Technical Framework Knowledge
#### Essential Tools and Frameworks
- Vercel AI SDK (if you are a typescript guy)
- LangChain (alternative option)
- Different models(openai, claude, gemini, etc, of course, now, deepseek. the temu in llm )
- Understanding of prompt engineering
#### Multi-Agent Systems
- Agents can communicate through natural language
- Inter-agent communication requires careful system design
- Implementation of thought processes and decision-making loops
- Safety considerations for system commands and operations
### 4. Language and Localization Considerations
- System prompts typically work best in English
- Multi-language support requires careful handling:
- Input translation to English
- Processing in English
- Output translation to target language
- Model performance varies across different languages
### 5. Safety and Error Handling
- Implementing validation layers for critical operations
- Understanding model limitations and potential errors
- Building feedback mechanisms to detect misunderstandings
## Conclusion
Transitioning from software engineering to AI engineering requires a significant mindset shift. While traditional software engineering skills remain valuable, understanding probabilistic systems, language models, and AI-specific architectures is crucial. The key is to balance innovation with practical safety considerations, especially when dealing with critical applications.
Remember that AI systems are not perfect, and building robust applications requires careful consideration of their limitations and appropriate safety measures. Start with existing frameworks and gradually build up complexity as you become more comfortable with AI-specific concepts and challenges.(the conclusion part is written by chatgpt, did you notice? :))
-

@ 97c70a44:ad98e322
2025-01-30 17:15:37
There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
# It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
# It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
# It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
# It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the *protocol*, while apps that benefit nostr exclusively via network effect are integrated into nostr the *network*. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency _as nostr users_.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
> Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
_As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria._
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a [spec](https://github.com/nostr-protocol/nips/pull/1190) for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
# It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
# Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (*ahem*, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the [nips repo](https://github.com/nostr-protocol/nips). No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-

@ 2183e947:f497b975
2025-02-13 04:44:45
# How Coinpools Improve Bitcoin
# Problems with bitcoin
UX problems with base layer payments include:
- Mining fees are sometimes high
- Confirmations usually take several minutes
- Using it privately requires running a coinjoin server
UX problems with lightning payments include:
- Setup fees are sometimes high
- Payments frequently fail
- Payments aren't asynchronous (the recipient has to stand there with their device open waiting to do a revoke_and_ack on their old state -- unless they use a custodian)
- Payments that *do* succeed occasionally take more than 30 seconds (due to stuck payments, automatic retries, and no ability to say "stop retrying" in any existing wallets that I'm aware of)
- Using it privately requires manual channel management
# Solutions
A lot of my recent work focuses on non-interactive coinpools. I figured out a way to do them on bitcoin if we had CTV + CSFS, and then, with a bit more thought, I figured out that my model didn't actually require those things, so I am now working on an implementation. But my model does benefit a lot from CTV (less sure about CSFS at this point) so let me outline how non-interactive coinpools fix the above problems and along the way I will share how CTV specifically improves coinpools.
## "Mining fees are sometimes high"
Coinpools improve the problem of "mining fees are sometimes high" by letting you bypass them in more cases. If you're in a coinpool and pay someone else in the same coinpool, your payment does not show up on the base layer, it just involves modifying some unilateral withdrawal transactions such that the sender can withdraw less and the recipient can withdraw more. The transactions are off-chain, like LN transactions, so you can do that without paying a base layer fee.
## "Confirmations usually take several minutes"
Coinpools improve the problem of "confirmations usually take several minutes" in a similar manner. Payments *inside* a coinpool (i.e. to another pool user) merely involve modifying off-chain data (and revoking an old state), so they can be as fast as lightning. In most cases I expect them to be a bit faster because there's less need for pathfinding or negotiating with a variety of routing nodes. If the sender and the recipient are in the same pool, they only need to talk to each other and, in my model, a coordinator.
## "Using the base layer privately requires running a coinjoin server"
Coinpools improve the problem of "using the base layer privately requires running a coinjoin server" in two ways: first, if you're in a coinpool and you send money to a bitcoin address, the blockchain doesn't know which coinpool user sent that payment. Analysts might be able to trace the payment to the coinpool, but from the blockchain's perspective, that's just a multisig; the actual person *inside* the multisig who sent the money is not revealed. However, my model uses a coordinator, and the coordinator probably knows which user sent the payment. Still, only 1 person knowing is better than having everyone on the blockchain know.
Second, if you send money to someone *inside* the coinpool, in my model, the only people who know about your payment are the sender, the recipient, and the coordinator, and the recipient does not know who the sender is. Moreover, my model allows users to act as bridges from LN to other pool users, so even the coordinator doesn't know if the person who *looks* like the sender was the *real* sender or just a bridge node, with the *real* sender being someone on lightning.
## "Setup fees on lightning are sometimes high"
Coinpools improve the problem of "setup fees are sometimes high" by having multiple users share the setup cost. My model allows a single bitcoin transaction to fund a coinpool with a number of members between 1 and probably about 100. (The max I've actually successfully tested is 11.) If the users share the cost of that transaction, then even in a high fee scenario, where bitcoin transactions cost $50, each user only has to pay a fraction of that, where the fraction is determined by how many users are joining the pool. If 10 people are joining, each user would pay $5 instead of $50. If 50 people are joining, each user would pay $1. If 100 people are joining, each user would pay 50¢.
## Sidebar: how CTV improves my coinpool model
The setup is also where CTV greatly improves my model. For my model to work, the users have to coordinate to create the pool in something I call a "signing ceremony," which is very similar to a coinjoin. The signing ceremony has to be scheduled and each user has to show up for it or they won't get into the pool. With CTV, you could fix this: instead of a signing ceremony, an exchange could autosend your money into a coinpool on e.g. a monthly basis and email you the data you need to perform your unilateral exit. All they need from you is a pubkey, and they can do everything else.
## "Lightning payments frequently fail"
Coinpools improve the problem of "payments frequently fail" by reducing the need for pathfinding, which is a typical cause of failure on lightning. If you are paying someone in the same pool as you, you always know an exact path: it will be you -> coordinator -> recipient. These short paths also reduce the likelihood of routing nodes having insufficient capacity to forward the payment. You've only got one "routing node" to worry about -- the coordinator.
## "Lightning payments aren't asynchronous"
Coinpools *in general* don't improve the problem of "payments aren't asynchronous" but my model in particular *does* improve that problem because I am combining it with my hedgehog protocol from last year, which *does* allow for asynchronous lightning-like payments. Relatedly, my coinpool model technically has a network model, it's just a hub-and-spoke network: the coordinator is connected to every user of the pool and can forward asynchronous hedgehog payments to them. This means you can send money to someone when they are offline; they'll get it whenever they *do* get online, even if *you* went offline in the meantime.
## "Lightning payments sometimes take too long"
Coinpools improve the problem of "stuck" lightning payments by reducing the number of hops along the route. As above, a payment inside the pool (per my model) is always just sender -> coordinator -> recipient. Due to only having 1 hop, there are fewer opportunities for a node to have a network issue and cause a delay.
## "Channel management is a pain"
Coinpools have multiple ways of improving the problem of manual channel management. In particular, not all coinpool models *have* channels, so channel management is not always needed in a coinpool. My model, however, does have channels, so channel management is still a thing.
Nonetheless, my model improves channel management in two ways: first, the setup costs are lower for the reasons given above. Second, payment asynchronicity helps for the following reason:
The worst pain point in channel management *today* occurs when someone sends you a payment but it fails because you didn't have enough inbound capacity. That doesn't happen in my coinpool model because payments are asynchronous. If you don't have enough inbound capacity, the payment doesn't fail, it just remains pending. So all you have to do is open a new channel (i.e. enter a new pool) and *then* finalize the payment.
## Zap me
I hope this essay clarifies why coinpools improve the problems I outlined and why CTV improves coinpools. I also hope this gets you a bit excited for my latest coinpool invention, which I hope to release soon :D (It really is very close to demo-ready.) If you liked this essay, consider zapping me: supertestnet@coinos.io
-

@ f1989a96:bcaaf2c1
2025-01-30 15:25:34
Good morning, readers!
This week, authoritarian regimes augmented their control and monitoring of online spaces in an attempt to suppress the dissenting voices of those they have financially repressed. While Pakistanis grapple with the highest cost of living in Asia, the military-backed regime passed an oppressive social media bill that empowers the government to imprison and fine individuals deemed to be spreading “disinformation” online.\
\
Meanwhile, in Belarus, authoritarian Alexander Lukashenko secured a seventh term in an openly rigged presidential election, further consolidating his grip on power and deepening the country’s political and financial repression. This prolongs his rule beyond three decades, cementing him as the sole ruler of Belarus since the country gained independence from the Soviet Union in 1991.
In freedom technology news, open-source developer Super Testnet released a new privacy tool called Hurricash. It lets multiple users lock funds together in a single Bitcoin Unspent Transaction Output (UTXO), allowing them to transact within the pool of users with greater privacy and efficiency. With greater liquidity and adoption, it could prove a useful tool for human rights activists seeking financial privacy. \
\
Additionally, Zaprite integrated BTCPay Server, enabling users to accept Bitcoin, Lightning, and fiat payments using self-custodial and self-hosted Bitcoin infrastructure. This is particularly valuable for nonprofits and activists in authoritarian regimes, where governments monitor and restrict financial activity.
We end with the latest episode of the “Money Matters” podcast, where Jack Mallers, CEO of Strike, interviews HRF Chief Strategy Officer Alex Gladstein to discuss the often overlooked connection between Bitcoin and financial freedom.
**Now, let’s jump right in!**
### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a)
## **GLOBAL NEWS**
#### **Belarus | Lukashenko Sweeps Openly Rigged Election Amid Financial Repression**
In Belarus, authoritarian leader Alexander Lukashenko [secured](https://www.newarab.com/news/belarus-lukashenko-extends-three-decade-rule-sham-election) a seventh term in an openly rigged presidential election. Lukashenko’s crusade against dissent and political opposition has left many citizens and opposition figures exiled, imprisoned, and financially repressed. Historically, his regime has frozen bank accounts, blocked foreign currency exchanges, and cut off independent media from funding. By wielding financial and political power, Lukashenko ensures that no real opposition can rise, turning Belarus into a country where even the illusion of democracy has disappeared. In these environments, Bitcoin and tools like [Lnp2pbot](https://lnp2pbot.com) (an HRF grantee) help Belarusians circumvent financial restrictions and transact in a currency that Lukashenko can’t control.
#### **Nigeria | Joins BRICS Economic Coalition**
Nigeria is expanding its financial repression both internationally and domestically. It recently [joined](https://archive.ph/ZQDlO) BRICS, an intergovernmental economic organization led by the Chinese and Russian regimes. For some, this raises concerns as Nigeria may deepen its authoritarian ways and further restrict individual financial freedoms. Member countries are each leaders in the development and implementation of central bank digital currencies (CBDCs), threatening individual financial autonomy as financial control is increasingly placed under the purview of authoritarian states. In parallel, the Nigerian regime plans to [distribute](https://nairametrics.com/2025/01/15/fg-to-distribute-n75000-cash-transfers-to-70-million-nigerians-by-2025/) a 75,000 naira ($48) “cash transfer” to the nation’s poorest citizens. This bid to alleviate poverty risks, while stoking inflation and compromising privacy, as the initiative relies on digital registration through the National Identity Number (NIN) system. Nigeria’s strategy of using both micro and macro financial controls limits open markets and curtails individual freedoms.
#### **Pakistan | Regime Passes Repressive Bill Targeting Online Spaces**
Pakistan’s military-backed regime [passed](https://apnews.com/article/pakistan-cyber-law-social-media-6de3a878c434abb154b91012bc9ca33c) a repressive social media bill that allows officials to imprison citizens for spreading “disinformation” online. Under this new law, officials can block “unlawful and offensive” content and remove users from social media at a time when Pakistanis are increasingly turning to online spaces to express discontent over regime-imposed economic hardships. Those “spreading disinformation” risk facing three years in prison and fines of up to 2 million rupees ($7,150) — a harsh penalty for citizens grappling with the [highest](https://www.firstpost.com/world/pakistan-tops-asia-in-living-costs-and-inflation-rates-report-reveals-13759245.html) cost of living on the continent. Further, social platforms must register with the Social Media Protection and Regulatory Authority to operate or risk a permanent ban. Censorship and Internet controls are sadly nothing new for Pakistanis since the regime has [blocked](https://timesofindia.indiatimes.com/world/pakistan/social-media-platform-x-shutdown-continues-for-eighth-day-in-pakistan/articleshow/107983076.cms) X during elections and enacted a nationwide [Internet firewall](https://www.aljazeera.com/news/2024/11/26/pakistan-tests-china-like-digital-firewall-to-tighten-online-surveillance) to suppress public discourse and action.
#### **Cuba | Salary of Baseball Player Buys a Carton of Eggs**
Cuba’s cost-of-living crisis is so [severe](https://havanatimes.org/cuba/the-salary-of-a-cuban-baseball-player-buys-a-carton-of-eggs/) that even the country’s top and most profitable athletes cannot make ends meet. Exemplifying this, the monthly salary of a professional baseball player in the National Series — Cuba’s premier sporting event — barely covers the cost of a carton of eggs, forcing them to [seek opportunities](https://www.reuters.com/world/americas/cubas-migratory-stampede-has-no-end-sight-2024-09-11/) elsewhere. With the Cuban peso in freefall, [several](https://havanatimes.org/cuba/the-salary-of-a-cuban-baseball-player-buys-a-carton-of-eggs/) players have resigned, citing financial hardships as the reason for leaving the sport they love. Their departures reflect a broader reality: wages across Cuba fail to keep pace with severe inflation caused by the Cuban regime’s continuous economic mismanagement. The state continues to enforce wages in the collapsing peso while requiring “MLC” credits to purchase high-quality food and goods in a system that pulls in foreign exchange from abroad while stealing from citizens at home.
#### **South Sudan | Regime Blocks Citizen Access to Social Media**
In South Sudan, rebel leader Salva Kiir Mayardit [directed](https://nation.africa/kenya/news/africa/south-sudan-shuts-down-social-media-for-three-months-4898628) the National Communication Authority (NCA) to block each citizen’s access to social media nationwide for up to three months, citing concerns over “public safety” and “mental health.” This decision follows violent videos of Sudanese armed forces attacking South Sudanese refugees in Sudan. Sudanese rights groups condemned the ban as a blatant act of censorship and an abuse of power. “The death of our South Sudanese in Sudan should not culminate in blocking social media, which is one of the ways many of us get information,” [said](https://nation.africa/kenya/news/africa/south-sudan-shuts-down-social-media-for-three-months-4898628) one Sudanese citizen. By restricting social media, the regime demonstrates a clear willingness to silence dissent, suppress information, and stifle transparency under the guise of “protection.” As Sudanese grapple with [rising](https://www.bloomberg.com/news/articles/2024-03-30/south-sudan-cracks-down-on-parallel-fx-market-to-fight-inflation?utm_campaign=socialflow-organic&utm_source=twitter&utm_medium=social&cmpid%3D=socialflow-twitter-africa&utm_content=africa) prices, the ban further isolates them, leaving little room to coordinate relief efforts, share grievances, or hold those in power accountable.
## RECOMMENDED CONTENT
#### **IMF Offers a Glimpse at the Perils of Central Bank Digital Currencies by J.D. Tuccille**
In this [article](https://reason.com/2024/12/18/imf-offers-a-glimpse-at-the-perils-of-central-bank-digital-currencies/) for [Reason Magazine](https://reason.com/), [J.D. Tuccille](https://x.com/JD_Tuccille) examines the dangers of central bank digital currencies (CBDCs) and their implications for financial independence and privacy. Drawing from the International Monetary Fund’s (IMF) “[CBDC Virtual Handbook](https://www.imf.org/en/Topics/fintech/central-bank-digital-currency/virtual-handbook),” Tuccille explains how CBDCs grant governments unprecedented control to monitor transactions, impose restrictions, and manipulate financial behavior. He contrasts these state-issued digital currencies with decentralized alternatives like Bitcoin, highlighting the stark differences in privacy and user freedom. You can read the complete analysis [here](https://reason.com/2024/12/18/imf-offers-a-glimpse-at-the-perils-of-central-bank-digital-currencies/). To learn more about CBDCs and the threats they pose to civil liberties and human rights, check out our [HRF’s CBDC Tracker](https://cbdctracker.hrf.org/).
## BITCOIN AND FREEDOM TECH NEWS
#### **Super Testnet | Launches Hurricash**
Bitcoin Developer [Super Testnet](https://github.com/supertestnet) released [Hurricash](https://github.com/supertestnet/hurricash), an experimental and open-source Bitcoin privacy protocol. Hurricash lets multiple users lock funds together in a single Bitcoin [Unspent Transaction Output](https://river.com/learn/bitcoins-utxo-model/) (UTXO), making their transactions more private. Users can then transact within the pool with greater efficiency and privacy. With greater liquidity and adoption, it could prove a useful tool for human rights defenders seeking financial privacy. Innovations like this could also pave the way for activists in many decades to afford trustless BTC transactions.
#### **Zaprite | Integrates BTCPay Server**
[Zaprite](https://zaprite.com/), a platform for accepting Bitcoin payments, recently [integrated](https://blog.zaprite.com/how-to-connect-btcpay-server/) [BTCPay Server](https://btcpayserver.org/), an open-source Bitcoin payment processor and HRF grantee. This integration allows users to accept Bitcoin, Lightning, and fiat payments (like USD) while maintaining full control over their funds — something Zaprite couldn’t afford on its own. By connecting with BTCPay Server, users can receive Bitcoin payments directly to their own self-hosted wallet and node, reducing censorship risks and enhancing financial independence. This is valuable for nonprofits, merchants, and activists in authoritarian regimes, where governments monitor, freeze, and restrict financial activity.
#### **Breez SDK | Implements Pay to BIP 353 Addresses**
The Breez Software Development Kit (SDK), a tool for integrating self-custodial Lightning payments into apps and services, now [supports](https://github.com/breez/breez-sdk-liquid/releases/tag/0.6.2) payments to [BIP 353](https://github.com/bitcoin/bips/blob/master/bip-0353.mediawiki) addresses. BIP 353 enables individuals with access to a domain the ability to create static, human-readable payment addresses (such as user@domain), instead of a long string of letters and numbers. This means an activist with a website can receive Bitcoin donations directly through their domain — if their wallet supports BIP 353. Several Bitcoin wallets already using the Breez SDK include [Cake Wallet](https://cakewallet.com/), [Blitz Wallet](https://blitz-wallet.com/), and [Klever Wallet](https://klever.io/). These static addresses make receiving Bitcoin easier, more private, and more censorship resistant, reducing surveillance risks and simplifying recurring payments.
#### **Ark Labs | Releases Wallet Software Development Kit**
[Ark](https://arklabs.to/), a protocol promising faster and cheaper transactions on Bitcoin, [released](https://blog.arklabs.to/introducing-the-ark-wallet-sdk-d1c77ce61cfc) a wallet software development kit (SDK). The SDK is aimed at helping developers more readily create Ark-compatible Bitcoin wallets that support both traditional Bitcoin payments and Ark’s instant transactions on mobile and desktop platforms. Protocols like Ark hold promise for greater transaction efficiency and improve its transaction capabilities for those who need it most.
#### **Tornado Cash | US District Court Reverses Sanctions**
A United States District Court [ruled](https://www.theblock.co/post/336319/us-court-rules-against-tornado-cash-sanctions-torn-cryptocurrency-surges-140) to reverse the sanctions on Tornado Cash, marking a major legal win for financial privacy in the digital asset space. This decision follows a previous Appeals Court [ruling](https://www.therage.co/fifth-circuit-lifts-tornado-cash-sanctions/?mc_cid=2d0b2336ed&mc_eid=8de40cf474) that found the Treasury overstepped its authority by sentencing the digital asset mixer under the International Emergency Economic Powers Act (IEEPA). The court determined that Tornado Cash’s smart contracts (self-executing lines of code) do not constitute “property,” making them ineligible for sanctions under existing laws. These rulings set a positive precedent for decentralized protocols and financial privacy in a world where these tools are desperately needed. Developers cannot work on privacy openly in dictatorships, so they need havens in liberal democracies.
#### **OpenSats | Announces Grants for Three Bitcoin Core Contributors**
OpenSats, a public nonprofit supporting open-source software and projects, [announced](https://opensats.org/blog/more-for-core) three new grants for Bitcoin Core contributors [L0rinc](https://github.com/l0rinc), [kevkevin](https://github.com/kevkevinpal), and [Daniela Brozzoni](https://github.com/danielabrozzoni). L0rinc will improve Bitcoin Core's performance and reliability by optimizing Initial Block Download (IBD), block storage, and database functionality. Kevkevin will enhance Bitcoin Core's stability, security, and usability by fixing bugs and reviewing pull requests. Finally, Daniela will review Bitcoin Core's code, adding features and improving test coverage. HRF is pleased to see the continued support of open-source developers from this [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) grantee.
#### **Bitcoin Chiang Mai | Bitcoin for Human Rights Meetup**
[Bitcoin Chiang Mai](https://www.bitcoinchiangmai.org/), a grassroots Bitcoin community in Thailand, will host a meetup [exploring](https://x.com/jimmykostro/status/1883393135436529844?s=46) Bitcoin’s role in human rights and financial freedom on Feb. 7, 2025. HRF Global Bitcoin Adoption Fellow Win Ko Ko Aung will discuss how Bitcoin empowers activists and communities under authoritarian rule, with a particular focus on Burmese citizens. Held in Burmese and English, the event will educate attendees on Bitcoin as a tool for escaping financial repression. If you have Burmese friends in Chiang Mai, share this opportunity with them. You can register [here](https://docs.google.com/forms/d/e/1FAIpQLScscuPhxba_Ma040Wwm9-ud7eODWVMpb_8RpFx-12yYbvfl5g/viewform).
## RECOMMENDED CONTENT
#### **Bitcoin and Freedom with Alex Gladstein**
In a special [episode](https://www.youtube.com/watch?v=hC93o30gUa8) of the “Money Matters” podcast, Jack Mallers, CEO of Strike, speaks with Alex Gladstein, chief strategy officer at HRF, to discuss the powerful link between Bitcoin and financial freedom. Gladstein unpacks how authoritarian regimes manipulate money to control the public and explains why open-source financial tools are critical for resisting oppression. His insights make a compelling case for financial sovereignty as a fundamental human right — and why Bitcoin remains the most effective tool to secure it.
*If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).*
*Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\
*Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)*
*The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*.
[**Subscribe to newsletter**](http://financialfreedomreport.org/)
[**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Visit our website**](https://hrf.org/programs/financial-freedom/)
-

@ a012dc82:6458a70d
2025-02-13 04:00:01
In the dynamic world of global finance, the interplay between traditional monetary policy and the burgeoning digital asset market is becoming increasingly prominent. The U.S. Federal Reserve's recent pivot towards a more accommodative monetary policy has sparked intense discussion among investors, economists, and cryptocurrency enthusiasts. This shift, characterized by an expected reduction in interest rates, is not just a routine adjustment but a significant move that could have far-reaching implications for various asset classes, including cryptocurrencies like Bitcoin. As we delve into this topic, we aim to unravel the complexities of the Fed's policy change and its potential ripple effects on Bitcoin, a digital asset that has been a subject of much intrigue and speculation.
**Table Of Content**
- Understanding the Fed's Policy Shift
- Impact on Traditional Financial Markets
- Bitcoin's Response to Monetary Easing
- Analyzing the Economic Backdrop
- Bitcoin: A Safe Haven or Risk Asset?
- Risks and Opportunities
- Conclusion
- FAQs
**Understanding the Fed's Policy Shift**
The Federal Reserve, the guardian of the U.S. monetary system, wields immense influence over global financial markets. Its recent signaling of a dovish turn – an expectation of 75 basis points in rate cuts by 2024 – marks a significant departure from its previous stance. This change is reflective of the Fed's response to a confluence of macroeconomic factors, such as fluctuating inflation rates, global economic uncertainties, and domestic financial stability concerns. The Fed's decisions are closely monitored as they set the tone for economic growth, inflation control, and financial market stability. In this context, the anticipated rate cuts suggest a strategic move to stimulate economic activity by making borrowing cheaper, thereby potentially boosting investment and consumption. However, this policy shift is not without its complexities and nuances, as it must balance the fine line between stimulating growth and controlling inflation.
**Impact on Traditional Financial Markets**
The ripple effects of the Fed's policy announcement were immediately felt across traditional financial markets. Stock markets, often seen as a barometer of economic sentiment, reacted positively, with indices like the Dow Jones Industrial Average reaching new heights. This surge reflects investors' optimism about the potential for increased corporate profits and economic growth in a lower interest rate environment. Similarly, the bond market experienced a significant rally, with yields on government securities falling as bond prices rose. This movement in the bond market is indicative of investors' expectations of a more accommodative monetary policy, which typically leads to lower yields on fixed-income securities. These market reactions underscore the pivotal role of central bank policies in shaping investor sentiment and the direction of financial markets. They also highlight the interconnectedness of various asset classes, as changes in monetary policy can have cascading effects across different sectors of the economy.
**Bitcoin's Response to Monetary Easing**
Bitcoin's reaction to the Fed's dovish turn has been a subject of keen interest. The cryptocurrency, which had been experiencing volatility, showed signs of recovery following the Fed's announcement. This response is indicative of Bitcoin's increasing correlation with broader financial market trends, a significant development given its history as an uncorrelated asset. Bitcoin's sensitivity to macroeconomic factors like central bank policies points to its growing integration into the mainstream financial ecosystem. However, this integration also means that Bitcoin is increasingly exposed to the same macroeconomic risks and uncertainties that affect traditional assets. The Fed's policy shift could potentially make Bitcoin more attractive to investors seeking non-traditional assets in a low-interest-rate environment. However, Bitcoin's complex dynamics, including its decentralized nature, limited supply, and regulatory landscape, add layers of complexity to its response to monetary policy changes.
**Analyzing the Economic Backdrop**
The economic backdrop against which the Fed's policy shift occurs is multifaceted and dynamic. On one hand, the U.S. economy has demonstrated resilience, with robust GDP growth and positive retail sales figures suggesting underlying strength. On the other hand, inflation, though moderated from its peak, remains a concern, hovering above the Fed's target. This economic duality presents a challenging scenario for policymakers, who must navigate the delicate balance between stimulating growth and containing inflation. For investors and market participants, this creates an environment of uncertainty, as they must decipher mixed signals from economic data and policy announcements. In this context, Bitcoin's role and response become even more intriguing, as it operates at the intersection of technology, finance, and macroeconomics.
**Bitcoin: A Safe Haven or Risk Asset?**
The debate over Bitcoin's classification as a safe haven or a risk asset is intensified by the Fed's easing stance. Traditionally, in a low-interest-rate environment, investors seek assets that can serve as hedges against inflation and currency devaluation. Gold has historically played this role, and Bitcoin, with its fixed supply and digital scarcity, has drawn comparisons to gold. However, Bitcoin's relatively short history and high volatility make it a more complex and potentially riskier asset. The Fed's dovish policy could enhance Bitcoin's appeal as an alternative investment, especially if traditional assets like bonds offer lower returns. However, Bitcoin's classification as a safe haven is still a matter of debate, with opinions divided on its long-term stability and value retention capabilities.
**Risks and Opportunities**
Investors considering Bitcoin in light of the Fed's policy change face a landscape filled with both risks and opportunities. The potential for a Bitcoin rally in a low-interest-rate environment is counterbalanced by the cryptocurrency's inherent volatility and regulatory uncertainties. Bitcoin's price movements can be dramatic and unpredictable, influenced by a range of factors from technological developments to geopolitical events. Additionally, the regulatory environment for cryptocurrencies is still evolving, with potential changes posing risks to Bitcoin's accessibility and value. Investors must also consider the broader global economic context, including actions by other central banks and international trade dynamics, which can impact Bitcoin's market movement.
**Conclusion**
The Federal Reserve's shift towards a more accommodative monetary policy in 2024 presents a fascinating scenario for Bitcoin and the broader cryptocurrency market. This development underscores the increasing relevance of digital assets in the global financial landscape and highlights the complex interplay between traditional monetary policies and emerging financial technologies. As Bitcoin continues to evolve and gain acceptance, its response to macroeconomic factors like central bank policies will be a critical area of focus for investors. In navigating this dynamic and uncertain environment, a cautious and well-informed approach is essential for those looking to explore the opportunities and navigate the challenges of cryptocurrency investments. The coming years promise to be a pivotal period in the maturation of Bitcoin as it responds to the shifting tides of global finance.
**FAQs**
**How does the Federal Reserve's easing stance impact Bitcoin?**
The Fed's shift towards lower interest rates can make riskier assets like Bitcoin more attractive to investors. This is because lower rates often lead to reduced yields on traditional investments, prompting investors to seek higher returns elsewhere.
**What is the significance of the Fed's 'dot plot' for Bitcoin investors?**
The 'dot plot' is a projection of interest rate movements by Federal Reserve members. A shift towards lower rates, as indicated in the recent dot plot, can signal a more accommodative monetary policy, potentially impacting Bitcoin's market as investors adjust their portfolios.
**Can Bitcoin be considered a safe haven asset in light of the Fed's policy?**
Bitcoin's role as a safe haven asset is debated. While its fixed supply and digital nature offer some safe haven characteristics, its volatility and regulatory uncertainties make it a complex choice compared to traditional safe havens like gold.
**What risks should Bitcoin investors consider in the context of the Fed's easing policy?**
Investors should be aware of Bitcoin's volatility, regulatory changes, and its sensitivity to macroeconomic factors. Additionally, global economic conditions and actions by other central banks can also influence Bitcoin's market.
**How does the economic backdrop influence Bitcoin's response to the Fed's policy?**
Economic factors like GDP growth, inflation rates, and retail sales impact investor sentiment and risk appetite, which in turn can affect Bitcoin's market. A strong economy might reduce the appeal of risk assets like Bitcoin, while economic uncertainties can increase their attractiveness.
**That's all for today**
**If you want more, be sure to follow us on:**
**NOSTR: croxroad@getalby.com**
**X: @croxroadnews.co**
**Instagram: @croxroadnews.co**
**Youtube: @croxroadnews**
**Store: https://croxroad.store**
**Subscribe to CROX ROAD Bitcoin Only Daily Newsletter**
**https://www.croxroad.co/subscribe**
***DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.***
-

@ 57d1a264:69f1fee1
2025-02-13 03:45:23

**What You Will Learn:**
- Understanding the concept of cybersecurity
- Networking Basics
- Operating Systems Overview
- Introduction to Kali Linux
- Threat Actors and Cyber Threats
- Ethical Hacking Techniques and Tools.
**How to Register:**
Use this link to Register.
https://forms.gle/L8AGLCWU4djwUXxz9
originally posted at https://stacker.news/items/884407
-

@ 9e69e420:d12360c2
2025-01-30 12:23:04
Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York.
DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million.
The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture.
Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry.
![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
-

@ f6488c62:c929299d
2025-02-13 02:39:41
Lowering interest rates is one of the tools that central banks use to manage the economy, especially during periods of inflation, which causes the prices of goods and services to rise. Lowering interest rates not only helps stimulate spending but can also foster sustainable growth in businesses and labor markets.
Access to Capital and Economic Stimulation
When interest rates are lowered, the public can access capital more easily. With lower interest rates, borrowing becomes less burdensome, giving individuals and businesses the opportunity to start new ventures or expand existing businesses. This leads to increased investment and spending, which in turn keeps the economy circulating and growing.
For instance, when people can easily borrow money to start a new business—such as an online store or a product manufacturing business—the increase in entrepreneurs and the availability of goods in the market will ensure that the supply is sufficient to meet consumer demand. This, in turn, prevents prices from rising too much due to a lack of supply.
Reducing Inflation by Increasing Supply
Increasing the supply of goods and services in the market can significantly help in controlling inflation. When there are more goods or services available to meet market demand, competition among producers will naturally drive prices down. This is the basic principle of market dynamics: when there’s enough supply, prices are less likely to increase, even in times of high demand.
In addition, increasing supply helps address shortages, which are one of the key drivers of rising prices. When there is enough product available to satisfy demand, inflationary pressures can be relieved, and prices can stabilize.
Redistributing Income and Reducing Inequality
Lower interest rates also play a crucial role in redistributing income within society. By making access to capital easier, especially for those with lower or middle incomes, the public’s purchasing power increases, which can stimulate spending on essential goods and services.
When people have more money in hand, they are better able to access necessary products. This boosts demand in the market. However, alongside this increased demand, sufficient supply is needed to prevent prices from rising uncontrollably, which can lead to inflation.
Moreover, supporting the population through welfare programs or initiatives that allow everyone to access education and investment opportunities helps individuals create products and value in the market. A diverse market with a variety of products increases production efficiency and helps mitigate economic inequality, ensuring a more balanced and inclusive economy.
Conclusion
Lowering interest rates and redistributing income effectively can stimulate economic growth and reduce inflation. This works by ensuring there is sufficient supply to meet market demand, while also providing capital that allows the public to start new businesses and generate new products in the market.
For sustainable long-term economic growth, managing inflation should go hand in hand with investing in infrastructure and ensuring wealth distribution. This ensures that everyone has equal access to opportunities, leading to steady economic growth without negatively impacting the majority of society.
In summary, lowering interest rates is a key tool in stimulating the economy and reducing inflation, especially when the economy faces imbalances. It not only increases supply, but also promotes income redistribution and the creation of an economy that is more equitable in the long run.
-

@ 3b7fc823:e194354f
2025-02-13 02:25:42
site:example.com
intitle:"index of"
inurl:admin
intext:"password"
site:example.com
site:.gov
site:.edu
site:*.mil
inurl:login
inurl:admin
inurl:dashboard
inurl:portal
intitle:"admin login"
intitle:"index of /"
intitle:"index of" "parent directory"
intitle:"index of" "backup"
filetype:pdf "confidential"
filetype:xls "username | password"
filetype:doc "top secret"
filetype:sql "database"
intext:"username" intext:"password"
intext:"login" intext:"password"
filetype:txt "passwords"
inurl:"viewerframe?mode="
inurl:"/view.shtml"
inurl:"/view/index.shtml"
intitle:"index of" "wp-config.php"
inurl:".git"
filetype:xls intext:"email"
filetype:csv intext:"email"
inurl:"/setup.cgi?next_file=netgear.cfg"
inurl:"/wificonf.html"
-

@ fd78c37f:a0ec0833
2025-02-13 02:24:48
In this edition, we invited Rafael from Bitcoin É Aqui to share the development of his community and its efforts in promoting Bitcoin adoption. From establishing a Bitcoin-friendly environment in Rolante to organizing and supporting events like the Bitcoin Spring Festival and KuchenFest, Rafael highlighted Bitcoin's impact on the local economy and tourism industry.
**YakiHonne**: Today, we are honored to invite Rafael from Bitcoin é Aqui to join us. Before we dive in, I'd like to take a moment to introduce YakiHonne and share a bit about what we do. YakiHonne is a decentralized media client built on the Nostr protocol that enables freedom of speech through technology. It empowers creators to create their own voice, assets, and features. It also allows features like smart widgets, verified notes, and focuses on long-form articles. Now today we'll be exploring more about the Bitcoin community. Rafael, could you please briefly introduce what sparked your interest in Bitcoin, and what motivated you to create this community?
**Rafael**:Like many, Stim's and his wife Camila's initial interest was in technology— a completely new way to transfer money with full self-custody. From the beginning, the project focused on the payment network, and at the time, they didn’t realize it would evolve into “A Project.”
**YakiHonne**: Could you share how your community got started, the strategies you used to attract members, and the early challenges you encountered?
**Rafael**:From the start, we were all about building a payment network. We began by paying our barber, gardener, and other service providers with Bitcoin. After a few close friends joined, word started to spread—even though some were worried about scams and Bitcoin's legality. To address these concerns, we held a talk at the City's Trade Association on how merchants could legally accept Bitcoin. We expected 5 to 10 friends, but over 60 merchants attended! Today, we’re proud to say that our city is the most Bitcoin-friendly in the world, with more than 40% of stores accepting it. From plumbers to supermarkets, it’s amazing to see our community featured on the BitcoinMap website.

**YakiHonne**: What principles guide the community, and how do you maintain trust and reliability in discussions?
**Rafael**:Like Bitcoin itself, decentralization is our core principle. The project "Bitcoin É Aqui" (loosely translated as "Bitcoin is Here") assists merchants in setting up Lightning wallets and offers best practices. However, every merchant is free to operate as they see fit—choosing whether to follow our advice or to use any wallet they prefer. Moreover, many experienced merchants help onboard newcomers, building trust through established networks and reinforcing our decentralized approach.
**YakiHonne**: How do you educate members and keep them updated on Bitcoin developments?
**Rafael**:We have a group chat where we post some news, but in Brazil, almost everyone already uses WhatsApp for communication, and news usually spreads through these groups, again highlighting the decentralized nature of the Project.
**YakiHonne**: What initiatives has the community undertaken to promote Bitcoin adoption, and what results have you seen?
**Rafael**:Of course, the rising coin value draws attention, but the main attraction is tourists coming to Rolante to learn about the project. Rolante was already famed for its natural wonders—majestic mountains and breathtaking waterfalls. Combined with Bitcoin’s innovative acceptance as a payment method, it has become an even stronger magnet for visitors.
**Rafael**:In Rolante, living completely on Bitcoin is a reality. Here, you'll find travel agencies, professional tour guides, and a variety of services—from department stores and opticians to real estate agents, construction companies, architects, furniture stores, building materials suppliers, and solar energy providers. In the healthcare sector, you can rely on pharmacies, massage therapists, physiotherapists, and advanced dental services; even the city hospital accepts Bitcoin as payment.

**YakiHonne**: What are the community’s goals for the next 6-12 months, and how do you see it evolving with Bitcoin’s growth?
**Rafael**:As a project, Bitcoin É Aqui doesn’t dictate what the community should do, but we support many events like Pizza Day, Bitcoin Spring Festival, Bier Rock, KuchenFest. One major event is the biennial Bitcoin Spring Festival (BSF). The Bitcoin Spring Festival (BSF) is a key event in the Rolante Bitcoin community, aimed at promoting Bitcoin adoption and circular economy development. This year, the festival focuses on "Bitcoinization," bringing together notable figures in the Bitcoin space to showcase a real Bitcoin economic ecosystem. During the event, all transactions will be conducted via the Lightning Network, with Coinos.io and Wallet Of Satoshi recommended. BSF is not just a celebration but a movement toward financial freedom.

**Rafael**:This March, Rolante will host its most traditional event, KuchenFest, celebrating the local traditional bread delicacy. The event centers around the sweet bread Cuca, bringing together candy makers and Cuca enthusiasts to share recipes, techniques, and stories. Additionally, the festival features live music, folk dances, and family activities, showcasing rich cultural traditions. We will help the event accept and promote the use of Bitcoin.
-

@ fd208ee8:0fd927c1
2025-01-23 15:31:24
## Planning Alexandria
People keep asking what features nostr:npub1s3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqd975wz has planned for #Alexandria, but they're not set in stone because we're an agile project.
What we do have, is lots of tickets on our Kanban boards and a naming scheme, where we use a famous person's last name, to signify the release goals.

### Gutenberg v 0.1.0
(after the inventor of the printing press)
will contain the features needed to read and write [NIP-62 Curated Publications](https://github.com/nostr-protocol/nips/pull/1600), as well as encompassing the complex infrastructure, architecture, documentation, and personnel we require to make this all run smoothly and look easy.

### Euler v 0.2.0
(after a mathematician credited with establishing graph theory)
will contain the features for deep-searching, visually exploring, and smartly navigating the data set, wiki page display, annotating and citing the publications, exporting to other formats (like PDF, ePUB, and LaTeX), and commenting/reviewing. To help with the heavy lifting, we will be swapping out the core with our own Nostr SDK called "Aedile".
### Defoe v 0.3.0
(after an author who perfected the novel format)
will be all about our favorite writers. We will be focusing upon profile data, payment systems, book clubs and communities, and stylesheets.
That is everything we have planned, for the v1.0 edition, and we consider that version to be a true product.
As for after that, a teaser...

-

@ 4506e04e:8c16ba04
2025-01-22 16:37:08
If you are a researcher in the field of medicine, you are most likely very familiar with PubMed – where you get citations for the articles and studies that drive your work forward. PubMed Central (PMC), the full-text repository of life sciences journal literature managed by the National Library of Medicine (NLM), was established in 2000. Its creation marked a significant milestone in providing open access to biomedical research. Since 2005, PMC has served as the designated repository for papers submitted under the NIH Public Access Policy, reflecting the growing emphasis on transparency and accessibility in scientific research. Over the years, PMC has expanded its scope, becoming a repository for papers aligned with public and open access policies from various research funding organizations, both within and beyond biomedical sciences.
## Funding and Partnerships
NLM’s operations, including PubMed and PMC, are supported by a combination of government funding and contributions from influential entities such as The Bill & Melinda Gates Foundation.
The Bill and Melinda Gates Foundation receives significant donations from pharmaceutical companies, as well as other organizations and individuals. The exact amount of money donated by each company can vary from year to year, but here are some examples of the amounts donated by the pharmaceutical companies:
**GSK (GlaxoSmithKline):**
- In 2020, GSK donated $100 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, GSK donated $50 million to the Gates Foundation to support the development of a new malaria vaccine.
**Pfizer:**
- In 2020, Pfizer donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, Pfizer donated $25 million to the Gates Foundation to support the development of a new malaria vaccine.
**Merck & Co.:**
- In 2020, Merck donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, Merck donated $25 million to the Gates Foundation to support the development of a new malaria vaccine.
**Novartis:**
- In 2020, Novartis donated $20 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis.
- In 2019, Novartis donated $10 million to the Gates Foundation to support the development of a new malaria vaccine.
**Johnson & Johnson:**
- In 2020, Johnson & Johnson donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, Johnson & Johnson donated $25 million to the Gates Foundation to support the development of a new malaria vaccine.
**Sanofi:**
- In 2020, Sanofi donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis.
- In 2019, Sanofi donated $10 million to the Gates Foundation to support the development of a new malaria vaccine.
**AstraZeneca:**
- In 2020, AstraZeneca donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis.
- In 2019, AstraZeneca donated $10 million to the Gates Foundation to support the development of a new malaria vaccine.
**Eli Lilly and Company:**
- In 2020, Eli Lilly donated $10 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis.
- In 2019, Eli Lilly donated $5 million to the Gates Foundation to support the development of a new malaria vaccine.
Additionally, NLM website [https://cdn.ncbi.nlm.nih.gov/pmc/cms/files/PMCFunderDepositList.xlsx] (list over 200)(!) organisations that are founding it. What could go wrong one might ask?!
## The Centralization Challenge
While PubMed and PMC have played a pivotal role in democratizing access to scientific literature, their centralized nature presents vulnerabilities. Over the past century healthcare has grown to become one of the most profitable industries and to believe that the healthcare system we have today is the best we can do is far from understatement.
PubMed's reliance on centralized funding and decision-making processes makes it susceptible to external influences, including lobbying by powerful entities. Moreover, the centralized infrastructure allows for content to be published and removed with relative ease, often without leaving a trace. This raises concerns about the integrity and permanence of the scientific record, particularly in contentious or politically sensitive areas of research.
The ability to alter or erase information from PubMed undermines trust in the system’s objectivity and neutrality. Researchers and the public alike depend on these repositories for reliable and impartial access to scientific knowledge. Any perceived or actual manipulation of content can erode confidence in the platform and compromise its foundational mission.
## The Case for Decentralization
To address these challenges, a decentralized alternative built on emerging technologies, such as the Nostr protocol, could offer significant advantages. A decentralized platform would:
- **Enhance Resilience:** By distributing data across a network of relays, a decentralized system would eliminate single points of failure, ensuring the scientific record remains intact and always accessible even in the face of technical or political disruptions.
- **Increase Transparency:** Decentralized systems inherently log changes, making it nearly impossible to alter or remove content without leaving an auditable trail. This transparency would bolster trust in the integrity of the research.
- **Reduce Susceptibility to Lobbying:** Without centralized control, the influence of external entities on the platform’s content would be significantly diminished, preserving the objectivity of the scientific record.
- **Foster Open Collaboration:** A decentralized approach aligns with the principles of open science, encouraging global collaboration without the constraints of centralized oversight or bias introduced by big pharma lobby.
## Conclusion
While PubMed and PMC have been instrumental in advancing access to scientific literature, their centralized nature leaves them vulnerable to manipulation and external pressures. A shift toward a decentralized, censorship-resistant platform would address these vulnerabilities and provide a more robust and trustless repository for scientific knowledge. Groundbreaking research that dares to challenge the pharmaceutical industry's status quo could be published anonymously, following in the footsteps of the Bitcoin whitepaper's pseudonymous author, Satoshi Nakamoto. Leveraging technologies like the Nostr protocol, the research community can build a system that ensures the permanence, integrity, and impartiality of the scientific record for generations to come.
-

@ ac6f9572:8a6853dd
2025-02-13 02:05:22
I attended Sats ‘n’ Facts to share my art, joining other Nostr artists in exhibiting our work at the event’s very first venue. It was a great opportunity to connect with fellow creatives, including Siritravelsketch, whose work I’ve admired on Nostr for some time. Meeting other artists in real life is always inspiring—there’s an undeniable creative bond that comes from sharing our passion in person.

Sats ‘n’ Facts is an Unconference, meaning there’s no strict schedule—everything is open for participants. It’s all about the connections made, the synergy shared, and, for the developers attending, the excitement of a hackathon. (A hackathon is an event where people collaborate intensively on engineering projects, often within 24 to 48 hours.)

My goal as an artist is to become a bridge between the Bitcoin tech world and the Bitcoin art and design space. Bitcoin empowers us by providing greater (financial) freedom, and with that freedom comes more time to pursue what we truly love—so in a way, you never have to “work” again. 😊

Nostr is a great example of how bubbles 🫧 POP, leading to new collaborations. Without tech, artists wouldn’t have a way to share their work, and without artists, creatives, and plebs, developers would have no one to build for. Both sides are essential for organic growth. This kind of synergy can only thrive in a decentralized system—otherwise, it risks being captured by big corporations. And that single point of failure is one of the biggest challenges we face in the world today.

Decentralization is freedom. Events like Sats ‘n’ Facts give us the opportunity to collaborate, create, and contribute to a more decentralized world—one where more people can truly become free.

Can’t wait to join the next Sats’n’facts. Maybe Barcelona!?
* * *
Originally article published by @BitPopArt on @YakiHonne: https://yakihonne.com/article/naddr1qvzqqqr4gupzqsa64uxz3ek0kx2mzlhqs0seavay4l06c4xek6a0zup8pmge8c6vqq242en0tukk7u2fwe8kkjrpv3ykgjtzwfsk5hmmfyp
#art #nostr #ThaiNostrich #artonnostr #artstr
originally posted at https://stacker.news/items/884327
-

@ df478568:2a951e67
2025-02-13 02:04:30
In the very early days, Nostr was pretty much troll-free. It was one of my favorite things about it, but I suspected this was only the case because only hardcore bitcoiners were on there. Now that the network is growing, there is more diversity of ideas. Ideology tends to make people mean. Mean people suck, so I try to remain respectful even when I disagree with others. I am not a fan of communism, but enjoy reading other perspectives. I do not wish to censor any speech at all, especially speech I do not agree with.
The freedom of speech is not about the First Amendment to me. It's about creating a space that is safe for free speech. Platforms are not a safe space for free speech. The safety of free speech is in peril on platforms. Nostr is a space where people can speak freely in an open Internet-connected society. There is some speech I would rather not see. I wish some people did not say certain things, but I do not want to stop them.
If we censor the worst speech, the speech does not go away. It merely goes underground and creates bad speech silos where people hide their true selves and go only speak to people just like them. Censorship is like prison for ideas. Prisoners improve their robbery skills because they exchange ideas with other criminals. It's like a conference for criminals. Fascists get more fascist when they only have permission to talk to fellow fascists. Communists get more communist when they can only talk to other communists. Ideas are a marketplace. May the best ideas win.
Nostr allows me to speak with people about topics I might not otherwise get a chance to speak about. I never see any pro-communist posts on Twitter. That's a problem because communists also don't see me. I also never saw sex workers talk about anything other than kinky-boinky talk on Twitter. Nostr brings the humanity back to sex workers. Sex workers are people too. They have interesting ideas and take [interesting photos]([take interesting pictures](nostr:note1svl3ne6l7dkxx4gckqsttx24nva7m37ynam7rvgq4zu83u9wl2ks86ahwx). )
On the [What is Money Show](https://fountain.fm/episode/DYPKRSkN11EmYDhrhH0H), Rabble says he wants to have Christians have a Christian-only Nostr network and sex workers to have a sex worker-only network. It's a fun idea, but I'm not convinced this would be a good thing. What if Jesus was on the Christian Nostr, but Mary Magdalen was on sex worker Nostr? I suspect Christians talking to sex workers is not such a bad thing. **What would Jesus do?**
Here is a conversation I had with a stripper on nostr. You can read the original [here](nostr:note1wxalrm6tpftrrs9rmzvv4e5gpnamkmfuu6fpwu9gs3wtudeegd7qpd5l0r) but I have reprinted it on the Habla and Substack.
I don't believe it's possible for a community or state to abolish private property when the private property can be distilled into 12 secret random words. Ironically, bitcoin does give the means of monetary production to the people, but this is a moot point given that individual people do not have equal ability. Very few people had sufficient knowledge to mine bitcoin when the block reward was 50 bitcoin every 10 minutes. Therefore, even though anybody could technically produce bitcoin blocks, very few people can.
The same is true for saving. Even if we could defy human nature with schemes such as this, it would not solve wealth inequality. Most people spend money like drunken sailors. If everyone had the same income that could not be debased or stolen, broke people would still exist because people do not have equal money management skills.
That is why I prefer capitalism with a non-socialist monetary system. The United States, contrary to popular belief, is not a capitalist economic system. It's a mixed economy where some people (banks and government) get money without doing any work aside from fudging numbers.
A bank does not save capital to buy a house. Banks print money to buy homes and collect rent from homeowners. It's an accounting trick, not capitalism.
Here's how capitalism works according to economist, Russ Roberts.
https://youtu.be/ljULutAUL7o?si=bLPY5IvwwMQvfXJK
npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
https://mempool.marc26z.com/block/00000000000000000001fa33d3d7750ed315d94e3c1def6512281b33bece333b
-

@ 16d11430:61640947
2025-01-21 20:40:22
In a world drowning in Monopoly money, where people celebrate government-mandated inflation as "economic growth," it takes a special kind of clarity—nay, cynicism—to rise above the fiat circus. This is your guide to shedding your fiat f**ks and embracing the serene chaos of sound money, all while laughing at the absurdity of a world gone fiat-mad.
---
1. Don’t Feed the Clowns
You know the clowns I’m talking about: central bankers in their tailored suits and smug smirks, wielding "tools" like interest rates and quantitative easing. Their tools are as real as a magician's wand, conjuring trillions of dollars out of thin air to keep their Ponzi economy afloat.
Rule #1: Don’t engage. If a clown offers you a hot take about the "strength of the dollar," smile, nod, and silently wonder how many cups of coffee their paycheck buys this month. Spoiler: fewer than last month.
---
2. Turn Off the Fiat News
Do you really need another breathless headline about the next trillion-dollar deficit? Or the latest clickbait on why you should care about the stock market's emotional rollercoaster? Mainstream media exists to distract you, to keep you tethered to their illusion of importance.
Turn it off. Replace it with something sound, like the Bitcoin whitepaper. Or Nietzsche. At least Nietzsche knew we were doomed.
---
3. Mock Their Inflationary Gospel
Fiat apologists will tell you that inflation is "necessary" and that 2% a year is a "healthy target." Sure, because a little robbery every year keeps society functioning, right? Ask them this: "If 2% is healthy, why not 20%? Why not 200%? Why not Venezuela?"
Fiat logic is like a bad acid trip: entertaining at first, but it quickly spirals into existential horror.
---
4. Celebrate the Fiat Freakshow
Sometimes, the best way to resist the fiat clown show is to revel in its absurdity. Watch politicians print money like teenagers running up a credit card bill at Hot Topic, then watch the economists applaud it as "stimulus." It’s performance art, really. Andy Warhol could never.
---
5. Build in the Chaos
While the fiat world burns, Bitcoiners build. This is the ultimate "not giving a fiat f**k" move: creating a parallel economy, one satoshi at a time. Run your Lightning node, stack sats, and laugh as the fiat circus consumes itself in a flaming pile of its own debt.
Let them argue about who gets to rearrange the deck chairs on the Titanic. You’re busy designing lifeboats.
---
6. Adopt a Fiat-Free Lifestyle
Fiat-free living means minimizing your entanglement with their clown currency. Buy meat, not ETFs. Trade skills, not IOUs. Tip your barber in Bitcoin and ask if your landlord accepts Lightning. If they say no, chuckle and say, “You’ll learn soon enough.”
Every satoshi spent in the real economy is a slap in the face to the fiat overlords.
---
7. Find the Humor in Collapse
Here’s the thing: the fiat system is unsustainable. You know it, I know it, even the clowns know it. The whole charade is destined to collapse under its own weight. When it does, find solace in the absurdity of it all.
Imagine the central bankers explaining hyperinflation to the public: "Turns out we can't print infinity after all." Pure comedy gold.
---
8. Stay Ruthlessly Optimistic
Despite the doom and gloom, there’s hope. Bitcoin is hope. It’s the lifeboat for humanity, the cheat code to escape the fiat matrix. Cynicism doesn’t mean nihilism; it means seeing the rot for what it is and choosing to build something better.
So, don’t just reject the fiat clown show—replace it. Create a world where money is sound, transactions are sovereign, and wealth is measured in energy, not debt.
---
Final Thought: Burn the Tent Down
Aldous Huxley once envisioned a dystopia where people are so distracted by their own hedonistic consumption that they don’t realize they’re enslaved. Sound familiar? The fiat clown show is Brave New World on steroids, a spectacle designed to keep you pacified while your wealth evaporates.
But here’s the punchline: they can only enslave you if you care. By rejecting their system, you strip them of their power. So let them juggle their debts, inflate their bubbles, and print their trillions. You’ve got Bitcoin, and Bitcoin doesn’t give a fiat f**k.
Welcome to the satirical resistance. Now go stack some sats.
-

@ 6be5cc06:5259daf0
2025-01-21 01:51:46
## Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
---
### Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado **gasto duplo**, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado **blockchain**, protegido por uma técnica chamada **Prova de Trabalho**. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
---
### 1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em **confiança**.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um **sistema de pagamento eletrônico baseado em provas matemáticas**, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o **Bitcoin**, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
---
### 2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
#### O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
#### Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
1. A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
2. Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
3. Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
#### Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
#### Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
---
### 3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
---
### 4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
---
### 5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
1. **Transmissão de Transações**: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
2. **Coleta de Transações em Blocos**: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
3. **Prova-de-Trabalho**: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
4. **Envio do Bloco Resolvido**: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
5. **Validação do Bloco**: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
6. **Construção do Próximo Bloco**: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
#### Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
#### Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
---
### 6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
#### Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
#### Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
#### Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
1. Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
2. Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
---
### 7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
---
### 8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
---
### 9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
#### Entradas e Saídas
Cada transação no Bitcoin é composta por:
- **Entradas**: Representam os valores recebidos em transações anteriores.
- **Saídas**: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como **troco**.
#### Exemplo Prático
Imagine que você tem duas entradas:
1. 0,03 BTC
2. 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- **Entrada**: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- **Saídas**: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
#### Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
---
### 10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando **chaves públicas anônimas**, que desvinculam diretamente as transações das identidades das partes envolvidas.
#### Fluxo de Informação
- No **modelo tradicional**, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No **Bitcoin**, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
#### Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
1. **Chaves Públicas Anônimas**: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
2. **Prevenção de Ligação**: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
#### Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações **multi-entrada** podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
---
### 11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
#### Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
#### A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem **80% do poder computacional** (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem **20% do poder computacional** (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
#### Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- **q** é o poder computacional do atacante (20%, ou 0,2).
- **p** é o poder computacional da rede honesta (80%, ou 0,8).
- **z** é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente **nulas**.
#### Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
#### Por Que Tudo Isso é Seguro?
- **A probabilidade de sucesso do atacante diminui exponencialmente.** Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- **A cadeia verdadeira (honesta) está protegida pela força da rede.** Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
#### E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
---
### 12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos.
A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos.
Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
---
Faça o download do whitepaper original em português:
https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-

@ ac6f9572:8a6853dd
2025-02-13 01:56:23

Date: 02/12/2025
One of the most efficient options to expand your knowledge and truly connect with people actively working in the space is through direct interactions, whether they’re happening at large conferences or smaller, semi-official meetups. But let’s be honest: finding all meaningful events can be a mess.
Take, for example, the '[BTC Events Map](https://docs.google.com/spreadsheets/d/1oni0QAHb2XYOL5gFVKHHGhG8w_HY5GDGBhdQ4SSrCZg/edit?gid=0&ref=europeanbitcoiners.com#gid=0),’ which already lists over 550 Bitcoin-only gatherings worldwide. This simple but very useful resource, put together by Satlantis, can help many of us plan our trips throughout the year. However, if you don’t know about its existence and rely solely on a search engine—whether Google or Brave—you’ll likely end up frustrated (and unfortunately missing many great opportunities to meet with others and learn).
Search for '_bitcoin events_,' and you’ll get a mix of irrelevant crypto, fintech, and Web3 results, with Bitcoin-related stuff buried somewhere in the middle, if at all.. Well, it’s really tough to find what you’re actually looking for.
That’s why word of mouth and trusted communities are so important. Sometimes, the best way to hear about an event is directly from people you know.
**One of those that flew under my radar was** [**SatsNFacts**](https://satsnfacts.btc.pub/?ref=europeanbitcoiners.com)**.**
It wasn’t listed on many typical event aggregators or any big news-promo sites. It mostly spread peer-to-peer and through the main channels on [Nostr](https://njump.me/npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx?ref=europeanbitcoiners.com).
I was ‘_lucky_’ enough to hear about it just in time to plan the trip from Europe to Thailand. Now, I’d like to briefly share my experience with you—everything that, in my opinion, made this event truly stand out.
**A Journey to Southeast Asia: Where Builders and Artists Collide.**
--------------------------------------------------------------------
Approximately 10,176 kilometers, 14 hours of travel, and finally three days spent at SatsNFacts—"Thailand’s first Bitcoin Technical Unconference”.
The event ran from February 8 to 10 in Chiang Mai (the largest city in northern Thailand). Held at Weave Artisan Society, a 700 sq.m venue that used to be an ice factory, it smoothly combined pleasant outdoors with an industrial-style, two-floor indoor area, creating a unique and very practical setup.
While its was billed as a “_Technical Unconference_,” in practice it nicely connected the developer-based ecosystem with different aspects of culture and art.
Each day, from 10 am to 6 pm, the agenda—shaped directly by attendees—was packed with various presentations, group chats, learning session, hackathons, and actionable workshops.
With many options available (around 10-20 topics per day), I couldn’t attend everything, but here are a few more technical sessions I joined and found especially worthwhile:
* **Liana Workshop** (long-term security, recovery, and inheritance),
* **TollGates** ([streaming sats for internet access](https://primal.net/e/naddr1qvzqqqr4gupzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68qq2nz63h0969vn2xwse9j3n5ge4xsdr2ddc4j0g960h?ref=europeanbitcoiners.com)),
* **Open Vault** (enterprise wallet interface),
* **Yaki Honne** ([decentralized media](https://yakihonne.com/?ref=europeanbitcoiners.com)),
* **Nostr Proxies** (Epoxy, WebSocket and relay monetization).
* **Silent payments** (simplified payment experiences without compromising privacy).
As mentioned earlier, SatsNFacts wasn’t just about Bitcoin tech. Some topics focused on community aspects as well. Two discussions I joined highlighted Bitcoin adoption ⚡ in for example Bali and Thailand, showing how sound money, integrity, and consistent work can solve real problems in these regions. Impressive stuff! Here you can learn more:
* [HuaiPhueng](https://geyser.fund/project/huaiphuengproject?hero=geyser&ref=europeanbitcoiners.com) on Geyser + "Bitcoin City" (their [short video](https://www.youtube.com/watch?feature=shared&v=211meP4liIo&ref=europeanbitcoiners.com)).
* Bitcoin Indonesia & Bitcoin House Bali ([all in one on GitHub](https://github.com/bitcoinindo21?ref=europeanbitcoiners.com))
Now, the art gallery, to continue with less technical aspects of SatsNFacts 🎨
This nicely-organized space located on the ground floor, near cozy coworking and networking spots, was for me a real gem. Indeed, adding a creative vibe to the entire event.
Around 30 unique works from local and international artists were on display, all inspired by themes of freedom and privacy. Though I don’t see myself as a typical _'artist_', I was honored to have some of my own pieces exhibited there as well (a short video below).
* * *
One of the highlights was meeting local Thai artists, especially [Siritravelsketch](https://njump.me/npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu?ref=europeanbitcoiners.com), who travelled six hours by train just one way to attend two days of the event.
Her stunning paintings, created using just a bamboo stick and ink, are deeply inspired by Thai architecture and culture. While some of her pre-prepared pieces hung in the gallery, she also painted a few new works on the spot during her visit. Truly spectacular!

* * *
I also had the chance to reconnect with [Satoshi Builds](https://njump.me/npub19m7m3rs66pfdn4ewhrm8slh60ukyxgrylaa03m73wa40j39lc03syq4gfu?ref=europeanbitcoiners.com), who made many great sketches during this event, and with [BitPopArt](https://njump.me/npub1gwa27rpgum8mr9d30msg8cv7kwj2lhav2nvmdwh3wqnsa5vnudxqlta2sz?ref=europeanbitcoiners.com), a Dutch artist who, just like me, chosen a nomadic lifestyle yet has been clearly considering Thailand his 'second home' as well for several years now. By the way, ✍️ here's his short summary of the event, focusing more on the artistic side of SatsNFacts: "[Art exhibition in Chiang Mai](https://bitpopart.com/2025/02/11/art-exhibition-in-chiang-mai/?ref=europeanbitcoiners.com)".
All in all, spending my time in many meaningful conversations and seeing so many deep artworks in one place filled me with hope and positive energy. THANK YOU, EVERYONE!

* * *
(presented artworks by for example: [Agi Choote](https://njump.me/npub1tlacuxmtv2wqud9qz0ujnr4mqavmnz3ayspfj93jr40tgf2mvu6seax3y7?ref=europeanbitcoiners.com), [Samhain](https://njump.me/npub1df47g7a39usamq83aula72zdz23fx9xw5rrfmd0v6p9t20n5u0ss2eqez9?ref=europeanbitcoiners.com), [Zed Erwan](https://njump.me/npub1r2sah0htqnw7xrs70gq00m48vp25neu8ym2n2ghrny92dqqf7sest8hth0?ref=europeanbitcoiners.com), [Existing Sprinkles](https://njump.me/npub1f5kc2agn63ecv2ua4909z9ahgmr2x9263na36jh6r908ql0926jq3nvk2u?ref=europeanbitcoiners.com), AZA 21m, BitPopArt.)
* * *
Mr. Rabbit in Thailand...
-------------------------
Monday, the final evening, and SatsNFacts got one more item on its agenda rooted in creative expression and independent art.
Representing [Bitcoin FilmFest](https://x.com/bitcoinfilmfest?ref=europeanbitcoiners.com) (a grassroots project created by an amazing group of freedom fighters and activists 🐇🧡), since I was the only one from our team in Thailand, in one of the rooms upstairs, I put together a mini cinematic experience.
Seven trailers and eleven shorts, including for example:
* NO MORE INFLATION, HUMMINGBIRD, PARALLEL SPACE, UNBANKABLE, THE LEGEND OF LANDI (🎬 some of the trailers).
* BITCOIN A NEW HOPE, SATOSHI NAKAMOTO - THE CREATOR OF BITCOIN, MAXIS CLUB SHOW - CHAPTER ONE, THE GREATEST HEIST IN HISTORY, HODL, THE ANATOMY OF BITCOIN – GENESIS BLOCK (📺 some of the presented shorts)
With around 10-15 participants, the response was positive, and we ended up spending an extra 10-maybe-20 minutes discussing the challenges and opportunities in Bitcoin-powered filmmaking, as well as the upcoming edition of [BFF25](https://bitcoinfilmfest.com/bff25/?ref=europeanbitcoiners.com) (the annual festival we're organizing this May in Warsaw, Poland).

**Substance Over Hype. Gatherings That Matter.**
------------------------------------------------
SatsNFacts made a solid reminder that Bitcoin events can help build a truly sovereign future while bringing together developers and artistic souls alike.
The mix of technical depth and creative energy—free from the shiny gossip that floods many social channels—made it a truly meaningful experience.
> SatsNFacts set a high standard, and I hope to see more events like it in the future. More unconferences, more cultural and community-driven gatherings.
**Here's to more signal, less noise!!!**
Big congrats to everyone who made the first SatsNFacts happen 👏 Respect especially to the organizers! You pulled off something truly special!
* * *
_BTC Your Mind. Let it Beat._
_Şela_ @AZA_21M
💡
Did you enjoy this article? Zap me some sats. No amount is small :) Lightning wallet: `aza21m@getalby.com`
- - -
Original Article: https://europeanbitcoiners.com/sats-and-facts-short-coverage-of-the-first-bitcoin-unconference-in-thailand/
#english #opinion #events #bitcoin #nostr #freedom #conference #siamstr #asia #thailand
-

@ 50809a53:e091f164
2025-01-20 22:30:01
For starters, anyone who is interested in curating and managing "notes, lists, bookmarks, kind-1 events, or other stuff" should watch this video:
https://youtu.be/XRpHIa-2XCE
Now, assuming you have watched it, I will proceed assuming you are aware of many of the applications that exist for a very similar purpose. I'll break them down further, following a similar trajectory in order of how I came across them, and a bit about my own path on this journey.
We'll start way back in the early 2000s, before Bitcoin existed. We had https://zim-wiki.org/
It is tried and true, and to this day stands to present an option for people looking for a very simple solution to a potentially complex problem. Zim-Wiki works. But it is limited.
Let's step into the realm of proprietary. Obsidian, Joplin, and LogSeq. The first two are entirely cloud-operative applications, with more of a focus on the true benefit of being a paid service. I will assume anyone reading this is capable of exploring the marketing of these applications, or trying their freemium product, to get a feeling for what they are capable of.
I bring up Obsidian because it is very crucial to understand the market placement of publication. We know social media handles the 'hosting' problem of publishing notes "and other stuff" by harvesting data and making deals with advertisers. But- what Obsidian has evolved to offer is a full service known as 'publish'. This means users can stay in the proprietary pipeline, "from thought to web." all for $8/mo.
See: https://obsidian.md/publish
THIS IS NOSTR'S PRIMARY COMPETITION. WE ARE HERE TO DISRUPT THIS MARKET, WITH NOTES AND OTHER STUFF. WITH RELAYS. WITH THE PROTOCOL.
Now, on to Joplin. I have never used this, because I opted to study the FOSS market and stayed free of any reliance on a paid solution. Many people like Joplin, and I gather the reason is because it has allowed itself to be flexible and good options that integrate with Joplin seems to provide good solutions for users who need that functionality. I see Nostr users recommending Joplin, so I felt it was worthwhile to mention as a case-study option. I myself need to investigate it more, but have found comfort in other solutions.
LogSeq - This is my "other solutions." It seems to be trapped in its proprietary web of funding and constraint. I use it because it turns my desktop into a power-house of note archival. But by using it- I AM TRAPPED TOO. This means LogSeq is by no means a working solution for Nostr users who want a long-term archival option.
But the trap is not a cage. It's merely a box. My notes can be exported to other applications with graphing and node-based information structure. Specifically, I can export these notes to:
- Text
- OPML
- HTML
- and, PNG, for whatever that is worth.
Let's try out the PNG option, just for fun. Here's an exported PNG of my "Games on Nostr" list, which has long been abandoned. I once decided to poll some CornyChat users to see what games they enjoyed- and I documented them in a LogSeq page for my own future reference. You can see it here:
https://i.postimg.cc/qMBPDTwr/image.png
This is a very simple example of how a single "page" or "list" in LogSeq can be multipurpose. It is a small list, with multiple "features" or variables at play. First, I have listed out a variety of complex games that might make sense with "multiplayer" identification that relies on our npubs or nip-05 addresses to aggregate user data. We can ALL imagine playing games like Tetris, Snake, or Catan together with our Nostr identities. But of course we are a long way from breaking into the video game market.
On a mostly irrelevant sidenote- you might notice in my example list, that I seem to be excited about a game called Dot.Hack. I discovered this small game on Itch.io and reached out to the developer on Twitter, in an attempt to purple-pill him, but moreso to inquire about his game. Unfortunately there was no response, even without mention of Nostr. Nonetheless, we pioneer on. You can try the game here: https://propuke.itch.io/planethack
So instead let's focus on the structure of "one working list." The middle section of this list is where I polled users, and simply listed out their suggestions. Of course we discussed these before I documented, so it is note a direct result of a poll, but actually a working interaction of poll results! This is crucial because it separates my list from the aggregated data, and implies its relevance/importance.
The final section of this ONE list- is the beginnings of where I conceptually connect nostr with video game functionality. You can look at this as the beginning of a new graph, which would be "Video Game Operability With Nostr".
These three sections make up one concept within my brain. It exists in other users' brains too- but of course they are not as committed to the concept as myself- the one managing the communal discussion.
With LogSeq- I can grow and expand these lists. These lists can become graphs. Those graphs can become entire catalogues of information than can be shared across the web.
I can replicate this system with bookmarks, ideas, application design, shopping lists, LLM prompting, video/music playlists, friend lists, RELAY lists, the LIST goes ON forever!
So where does that lead us? I think it leads us to kind-1 events. We don't have much in the way of "kind-1 event managers" because most developers would agree that "storing kind-1 events locally" is.. at the very least, not so important. But it could be! If only a superapp existed that could interface seamlessly with nostr, yada yada.. we've heard it all before. We aren't getting a superapp before we have microapps. Basically this means frameworking the protocol before worrying about the all-in-one solution.
So this article will step away from the deep desire for a Nostr-enabled, Rust-built, FOSS, non-commercialized FREEDOM APP, that will exist one day, we hope.
Instead, we will focus on simple attempts of the past. I encourage others to chime in with their experience.
Zim-Wiki is foundational. The user constructs pages, and can then develop them into books.
LogSeq has the right idea- but is constrained in too many ways to prove to be a working solution at this time. However, it is very much worth experimenting with, and investigating, and modelling ourselves after.
https://workflowy.com/ is next on our list. This is great for users who think LogSeq is too complex. They "just want simple notes." Get a taste with WorkFlowy. You will understand why LogSeq is powerful if you see value in WF.
I am writing this article in favor of a redesign of LogSeq to be compatible with Nostr. I have been drafting the idea since before Nostr existed- and with Nostr I truly believe it will be possible. So, I will stop to thank everyone who has made Nostr what it is today. I wouldn't be publishing this without you!
One app I need to investigate more is Zettlr. I will mention it here for others to either discuss or investigate, as it is also mentioned some in the video I opened with. https://www.zettlr.com/
On my path to finding Nostr, before its inception, was a service called Deta.Space. This was an interesting project, not entirely unique or original, but completely fresh and very beginner-friendly. DETA WAS AN AWESOME CLOUD OS. And we could still design a form of Nostr ecosystem that is managed in this way. But, what we have now is excellent, and going forward I only see "additional" or supplemental.
Along the timeline, Deta sunsetted their Space service and launched https://deta.surf/
You might notice they advertise that "This is the future of bookmarks."
I have to wonder if perhaps I got through to them that bookmarking was what their ecosystem could empower. While I have not tried Surf, it looks interested, but does not seem to address what I found most valuable about Deta.Space: https://webcrate.app/
WebCrate was an early bookmarking client for Deta.Space which was likely their most popular application. What was amazing about WebCrate was that it delivered "simple bookmarking." At one point I decided to migrate my bookmarks from other apps, like Pocket and WorkFlowy, into WebCrate.
This ended up being an awful decision, because WebCrate is no longer being developed. However, to much credit of Deta.Space, my WebCrate instance is still running and completely functional. I have since migrated what I deem important into a local LogSeq graph, so my bookmarks are safe. But, the development of WebCrate is note.
WebCrate did not provide a working directory of crates. All creates were contained within a single-level directory. Essentially there were no layers. Just collections of links. This isn't enough for any user to effectively manage their catalogue of notes. With some pressure, I did encourage the German developer to flesh out a form of tagging, which did alleviate the problem to some extent. But as we see with Surf, they have pioneered in another direction.
That brings us back to Nostr. Where can we look for the best solution? There simply isn't one yet. But, we can look at some other options for inspiration.
HedgeDoc: https://hedgedoc.org/
I am eager for someone to fork HedgeDoc and employ Nostr sign-in. This is a small step toward managing information together within the Nostr ecosystem. I will attempt this myself eventually, if no one else does, but I am prioritizing my development in this way:
1. A nostr client that allows the cataloguing and management of relays locally.
2. A LogSeq alternative with Nostr interoperability.
3. HedgeDoc + Nostr is #3 on my list, despite being the easiest option.
Check out HedgeDoc 2.0 if you have any interest in a cooperative Markdown experience on Nostr: https://docs.hedgedoc.dev/
Now, this article should catch up all of my dearest followers, and idols, to where I stand with "bookmarking, note-taking, list-making, kind-1 event management, frameworking, and so on..."
Where it leads us to, is what's possible. Let's take a look at what's possible, once we forego ALL OF THE PROPRIETARY WEB'S BEST OPTIONS:
https://denizaydemir.org/
https://denizaydemir.org/graph/how-logseq-should-build-a-world-knowledge-graph/
https://subconscious.network/
Nostr is even inspired by much of the history that has gone into information management systems. nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn I know looks up to Gordon Brander, just as I do. You can read his articles here: https://substack.com/@gordonbrander and they are very much worth reading! Also, I could note that the original version of Highlighter by nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft was also inspired partially by WorkFlowy.
About a year ago, I was mesmerized coming across SubText and thinking I had finally found the answer Nostr might even be looking for. But, for now I will just suggest that others read the Readme.md on the SubText Gtihub, as well as articles by Brander.
Good luck everyone. I am here to work with ANYONE who is interested in these type of solution on Nostr.
My first order of business in this space is to spearhead a community of npubs who share this goal. Everyone who is interested in note-taking or list-making or bookmarking is welcome to join. I have created an INVITE-ONLY relay for this very purpose, and anyone is welcome to reach out if they wish to be added to the whitelist. It should be freely readable in the near future, if it is not already, but for now will remain a closed-to-post community to preemptively mitigate attack or spam. Please reach out to me if you wish to join the relay. https://logstr.mycelium.social/
With this article, I hope people will investigate and explore the options available. We have lots of ground to cover, but all of the right resources and manpower to do so. Godspeed, Nostr.
#Nostr #Notes #OtherStuff #LogSec #Joplin #Obsidian
-

@ cff1720e:15c7e2b2
2025-01-19 17:48:02
**Einleitung**\
\
Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\
Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie <roland@pareto.space> können sie sogar jederzeit umziehen, egal wohin. **Cool, das ist state of the art!** Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.

**Warum Nostr?**
Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz **"unserer Demokratie”** praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.

Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \
\
**Resümee:** keine Standards, keine Daten, keine Rechte = keine Zukunft!

\
**Wie funktioniert Nostr?**
Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum **“single point of failure”**, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\
\
Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. <roland@pareto.space> ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\
\
**Resümee:** ein offener Standard, alle Daten, alle Rechte = große Zukunft!

\
**Warum ist Nostr die Zukunft des Internet?**
“Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie **(Value4Value)**. OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.

\
**Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.**
<https://nostr.net/> \
<https://start.njump.me/>
**Hier das Interview zum Thema mit Radio Berliner Morgenröte**
<https://www.podbean.com/ew/pb-yxc36-17bb4be>
-

@ ac6f9572:8a6853dd
2025-02-13 01:55:20
# Freedom Tech, Privacy, Sound Money, and Culture: How to Find Your Tribe?
> Keeping up with everything happening in Bitcoin isn’t easy, even if you’ve been around for a while. The pace is relentless: stream of events, discussions, projects, and updates, not to mention the noise on social media...

Date: 02/12/2025
One of the most efficient options to expand your knowledge and truly connect with people actively working in the space is through direct interactions, whether they’re happening at large conferences or smaller, semi-official meetups. But let’s be honest: finding all meaningful events can be a mess.
Take, for example, the '[BTC Events Map](https://docs.google.com/spreadsheets/d/1oni0QAHb2XYOL5gFVKHHGhG8w_HY5GDGBhdQ4SSrCZg/edit?gid=0&ref=europeanbitcoiners.com#gid=0),’ which already lists over 550 Bitcoin-only gatherings worldwide. This simple but very useful resource, put together by Satlantis, can help many of us plan our trips throughout the year. However, if you don’t know about its existence and rely solely on a search engine—whether Google or Brave—you’ll likely end up frustrated (and unfortunately missing many great opportunities to meet with others and learn).
Search for '_bitcoin events_,' and you’ll get a mix of irrelevant crypto, fintech, and Web3 results, with Bitcoin-related stuff buried somewhere in the middle, if at all.. Well, it’s really tough to find what you’re actually looking for.
That’s why word of mouth and trusted communities are so important. Sometimes, the best way to hear about an event is directly from people you know.
**One of those that flew under my radar was** [**SatsNFacts**](https://satsnfacts.btc.pub/?ref=europeanbitcoiners.com)**.**
It wasn’t listed on many typical event aggregators or any big news-promo sites. It mostly spread peer-to-peer and through the main channels on [Nostr](https://njump.me/npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx?ref=europeanbitcoiners.com).
I was ‘_lucky_’ enough to hear about it just in time to plan the trip from Europe to Thailand. Now, I’d like to briefly share my experience with you—everything that, in my opinion, made this event truly stand out.
**A Journey to Southeast Asia: Where Builders and Artists Collide.**
--------------------------------------------------------------------
Approximately 10,176 kilometers, 14 hours of travel, and finally three days spent at SatsNFacts—"Thailand’s first Bitcoin Technical Unconference”.
The event ran from February 8 to 10 in Chiang Mai (the largest city in northern Thailand). Held at Weave Artisan Society, a 700 sq.m venue that used to be an ice factory, it smoothly combined pleasant outdoors with an industrial-style, two-floor indoor area, creating a unique and very practical setup.
While its was billed as a “_Technical Unconference_,” in practice it nicely connected the developer-based ecosystem with different aspects of culture and art.
Each day, from 10 am to 6 pm, the agenda—shaped directly by attendees—was packed with various presentations, group chats, learning session, hackathons, and actionable workshops.
With many options available (around 10-20 topics per day), I couldn’t attend everything, but here are a few more technical sessions I joined and found especially worthwhile:
* **Liana Workshop** (long-term security, recovery, and inheritance),
* **TollGates** ([streaming sats for internet access](https://primal.net/e/naddr1qvzqqqr4gupzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68qq2nz63h0969vn2xwse9j3n5ge4xsdr2ddc4j0g960h?ref=europeanbitcoiners.com)),
* **Open Vault** (enterprise wallet interface),
* **Yaki Honne** ([decentralized media](https://yakihonne.com/?ref=europeanbitcoiners.com)),
* **Nostr Proxies** (Epoxy, WebSocket and relay monetization).
* **Silent payments** (simplified payment experiences without compromising privacy).
As mentioned earlier, SatsNFacts wasn’t just about Bitcoin tech. Some topics focused on community aspects as well. Two discussions I joined highlighted Bitcoin adoption ⚡ in for example Bali and Thailand, showing how sound money, integrity, and consistent work can solve real problems in these regions. Impressive stuff! Here you can learn more:
* [HuaiPhueng](https://geyser.fund/project/huaiphuengproject?hero=geyser&ref=europeanbitcoiners.com) on Geyser + "Bitcoin City" (their [short video](https://www.youtube.com/watch?feature=shared&v=211meP4liIo&ref=europeanbitcoiners.com)).
* Bitcoin Indonesia & Bitcoin House Bali ([all in one on GitHub](https://github.com/bitcoinindo21?ref=europeanbitcoiners.com))
Now, the art gallery, to continue with less technical aspects of SatsNFacts 🎨
This nicely-organized space located on the ground floor, near cozy coworking and networking spots, was for me a real gem. Indeed, adding a creative vibe to the entire event.
Around 30 unique works from local and international artists were on display, all inspired by themes of freedom and privacy. Though I don’t see myself as a typical _'artist_', I was honored to have some of my own pieces exhibited there as well (a short video below).
* * *
One of the highlights was meeting local Thai artists, especially [Siritravelsketch](https://njump.me/npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu?ref=europeanbitcoiners.com), who travelled six hours by train just one way to attend two days of the event.
Her stunning paintings, created using just a bamboo stick and ink, are deeply inspired by Thai architecture and culture. While some of her pre-prepared pieces hung in the gallery, she also painted a few new works on the spot during her visit. Truly spectacular!

* * *
I also had the chance to reconnect with [Satoshi Builds](https://njump.me/npub19m7m3rs66pfdn4ewhrm8slh60ukyxgrylaa03m73wa40j39lc03syq4gfu?ref=europeanbitcoiners.com), who made many great sketches during this event, and with [BitPopArt](https://njump.me/npub1gwa27rpgum8mr9d30msg8cv7kwj2lhav2nvmdwh3wqnsa5vnudxqlta2sz?ref=europeanbitcoiners.com), a Dutch artist who, just like me, chosen a nomadic lifestyle yet has been clearly considering Thailand his 'second home' as well for several years now. By the way, ✍️ here's his short summary of the event, focusing more on the artistic side of SatsNFacts: "[Art exhibition in Chiang Mai](https://bitpopart.com/2025/02/11/art-exhibition-in-chiang-mai/?ref=europeanbitcoiners.com)".
All in all, spending my time in many meaningful conversations and seeing so many deep artworks in one place filled me with hope and positive energy. THANK YOU, EVERYONE!

* * *
(presented artworks by for example: [Agi Choote](https://njump.me/npub1tlacuxmtv2wqud9qz0ujnr4mqavmnz3ayspfj93jr40tgf2mvu6seax3y7?ref=europeanbitcoiners.com), [Samhain](https://njump.me/npub1df47g7a39usamq83aula72zdz23fx9xw5rrfmd0v6p9t20n5u0ss2eqez9?ref=europeanbitcoiners.com), [Zed Erwan](https://njump.me/npub1r2sah0htqnw7xrs70gq00m48vp25neu8ym2n2ghrny92dqqf7sest8hth0?ref=europeanbitcoiners.com), [Existing Sprinkles](https://njump.me/npub1f5kc2agn63ecv2ua4909z9ahgmr2x9263na36jh6r908ql0926jq3nvk2u?ref=europeanbitcoiners.com), AZA 21m, BitPopArt.)
* * *
Mr. Rabbit in Thailand...
-------------------------
Monday, the final evening, and SatsNFacts got one more item on its agenda rooted in creative expression and independent art.
Representing [Bitcoin FilmFest](https://x.com/bitcoinfilmfest?ref=europeanbitcoiners.com) (a grassroots project created by an amazing group of freedom fighters and activists 🐇🧡), since I was the only one from our team in Thailand, in one of the rooms upstairs, I put together a mini cinematic experience.
Seven trailers and eleven shorts, including for example:
* NO MORE INFLATION, HUMMINGBIRD, PARALLEL SPACE, UNBANKABLE, THE LEGEND OF LANDI (🎬 some of the trailers).
* BITCOIN A NEW HOPE, SATOSHI NAKAMOTO - THE CREATOR OF BITCOIN, MAXIS CLUB SHOW - CHAPTER ONE, THE GREATEST HEIST IN HISTORY, HODL, THE ANATOMY OF BITCOIN – GENESIS BLOCK (📺 some of the presented shorts)
With around 10-15 participants, the response was positive, and we ended up spending an extra 10-maybe-20 minutes discussing the challenges and opportunities in Bitcoin-powered filmmaking, as well as the upcoming edition of [BFF25](https://bitcoinfilmfest.com/bff25/?ref=europeanbitcoiners.com) (the annual festival we're organizing this May in Warsaw, Poland).

**Substance Over Hype. Gatherings That Matter.**
------------------------------------------------
SatsNFacts made a solid reminder that Bitcoin events can help build a truly sovereign future while bringing together developers and artistic souls alike.
The mix of technical depth and creative energy—free from the shiny gossip that floods many social channels—made it a truly meaningful experience.
> SatsNFacts set a high standard, and I hope to see more events like it in the future. More unconferences, more cultural and community-driven gatherings.
**Here's to more signal, less noise!!!**
Big congrats to everyone who made the first SatsNFacts happen 👏 Respect especially to the organizers! You pulled off something truly special!
* * *
_BTC Your Mind. Let it Beat._
_Şela_ @AZA_21M
💡
Did you enjoy this article? Zap me some sats. No amount is small :) Lightning wallet: `aza21m@getalby.com`
- - -
Original Article: https://europeanbitcoiners.com/sats-and-facts-short-coverage-of-the-first-bitcoin-unconference-in-thailand/
#english #opinion #events #bitcoin #nostr #freedom #conference #siamstr #asia #thailand
originally posted at https://stacker.news/items/884317
-

@ fd208ee8:0fd927c1
2025-01-19 12:10:10
I am so tired of people trying to waste my time with Nostrized imitations of stuff that already exists.
Instagram, but make it Nostr.
Twitter, but make it Nostr.
GitHub, but make it Nostr.
Facebook, but make it Nostr.
Wordpress, but make it Nostr.
GoodReads, but make it Nostr.
TikTok, but make it Nostr.
That stuff already exists, and it wasn't that great the first time around, either. Build something better than that stuff, that can only be brought into existence because of Nostr.
Build something that does something completely and awesomely new. Knock my socks off, bro.
Cuz, ain't nobody got time for that.
-

@ 1cb14ab3:95d52462
2025-02-13 01:30:00
**Dirt, body weight. [125' x 2']**
*This project was exhibited in 2015 in Boulder, Colorado.*
---
### Artist Statement
“A Line Made By Walking” (2015) is a site-specific piece created in Boulder, CO, where my body weight etched a temporary line into the earth. This work pays homage to Richard Long’s seminal 1967 piece, where a simple act of walking through the landscape left a profound trace. In my version, the line created by my movement forces the viewer to engage with the impermanence of human intervention on the land. The project prompts a reflection on the subtle yet lasting impacts we have on the environment, even through seemingly minimal actions.
As part of my larger “[Rockway](https://hes.npub.pro/post/1708400183541/)” project, this case study explores the concept of ‘line’ in both literal and metaphorical ways. The line is not just a physical mark, but also a representation of time, movement, and the dialogue between the body and the land. Walking, in this context, becomes a way of marking time—an act that is as ephemeral as the mark it leaves behind. The work questions the tension between permanence and transience, asking the viewer to consider how we interact with the land, both intentionally and unknowingly, and how those interactions leave traces that may soon fade but never completely disappear.
---
### Photos







---
#### More Land Art:
[Earth Lens Series](https://hes.npub.pro/post/1731091744332/)
["Looking Glass"](https://hes.npub.pro/post/1736304563962/)
["Het Bonhe"](https://hes.npub.pro/post/1720242458557/)
["Rockway"](https://hes.npub.pro/post/1708400183541/)
["Invasive"](https://hes.npub.pro/post/1719722211094/)
---
#### More from Hes
[Full Portfolio](https://hesart.npub.pro)
[Online Store](https://plebeian.market/community/hes@nostrplebs.com/hesmart-ym3fcufdfz)
[Artist Statements](https://hes.npub.pro/tag/art/)
[Travel Guides](https://hes.npub.pro/tag/travel/)
[Photography](https://hes.npub.pro/tag/photography)
[Writings](https://hes.npub.pro/tag/money)
---
*All images are credit of Hes, but you are free to download and use for any purpose. If you find joy from my art, please feel free to send a zap. Enjoy life on a Bitcoin standard.*
-

@ 20e7c953:3b8bcb21
2025-02-13 01:15:42
Biggest takeaway? We needed more hands to cover key roles - something to improve for next time, if there is any! That said, the strongest point was the organic networking and building, which set this apart from more structured, commercial conferences.
For future events - if any! - Hackathons will need dedicated time slots in the future, given the time constraints. The art side of things isn’t over yet—the exhibition will keep going for another month.
The event started a bit messy, but the quality of people made it flow naturally, creating a unique and engaging atmosphere. Overall, a great experience, and we’ll keep iterating for the next one.
We’ll send out a survey soon to gather more feedback. Huge thanks to our sponsors and media partners for making this happen - appreciate the support.
On Communities:
Lastly, while both commercial and less commercial events are needed there is something that doesn't beat Bitcoin Culture which are Bitcoin-only Meetups.
If we are in a position to give some advice: Make sure you engage with your local community since people behind it are most likely the ones who can able to bootstrap new comers while keeping trust and accountability in place.
Luckily today we have most tools to filter out those who are leeching off others PoW and the genuine ones trailblazing on their own terms. On our side definitely one of the biggest lessons learnt was to work with the local Communities for future events - regardless - this time we managed to get it done with our hands, will and not much else since *most* tools used have been FOSS and that's why we are here for !
With that said and while continuously gathering more feedback these coming days....
WHAT DID YOU ENJOYED THE MOST?
ANYTHING YOU DISLIKED?
**WHERE SHOULD WE HOST SATS N FACTS NEXT ?👀**
SUGGESTIONS AND FEEDBACK MAILBOX IS OPEN 📬
Onwards 🫡
-

@ f9cf4e94:96abc355
2025-01-18 06:09:50
Para esse exemplo iremos usar:
| Nome | Imagem | Descrição |
| --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ |
| Raspberry PI B+ |  | **Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2,** |
| Pen drive |  | **16Gb** |
Recomendo que use o **Ubuntu Server** para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi [aqui]( https://ubuntu.com/download/raspberry-pi). O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível [aqui]( https://ubuntu.com/tutorials/how-to-install-ubuntu-on-your-raspberry-pi). **Não instale um desktop** (como xubuntu, lubuntu, xfce, etc.).
---
## Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
```bash
apt update
apt install tor
```
---
## Passo 2: Criar o Arquivo de Serviço `nrs.service` 🔧
Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit
[Unit]
Description=Nostr Relay Server Service
After=network.target
[Service]
Type=simple
WorkingDirectory=/opt/nrs
ExecStart=/opt/nrs/nrs-arm64
Restart=on-failure
[Install]
WantedBy=multi-user.target
```
---
## Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr [aqui no GitHub]( https://github.com/gabrielmoura/SimpleNosrtRelay/releases).
---
## Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
```bash
mkdir -p /opt/nrs /mnt/edriver
```
---
## Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
```bash
lsblk
```
---
## Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo, `/dev/sda`) e formate-o:
```bash
mkfs.vfat /dev/sda
```
---
## Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta `/mnt/edriver`:
```bash
mount /dev/sda /mnt/edriver
```
---
## Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
```bash
blkid
```
---
## Passo 9: Alterar o `fstab` para Montar o Pendrive Automáticamente 📝
Abra o arquivo `/etc/fstab` e adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:
```fstab
UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
```
---
## Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta `/opt/nrs`:
```bash
cp nrs-arm64 /opt/nrs
```
---
## Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em `/opt/nrs/config.yaml`:
```yaml
app_env: production
info:
name: Nostr Relay Server
description: Nostr Relay Server
pub_key: ""
contact: ""
url: http://localhost:3334
icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png
base_path: /mnt/edriver
negentropy: true
```
---
## Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo `nrs.service` para o diretório `/etc/systemd/system/`:
```bash
cp nrs.service /etc/systemd/system/
```
Recarregue os serviços e inicie o serviço `nrs`:
```bash
systemctl daemon-reload
systemctl enable --now nrs.service
```
---
## Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor `/var/lib/tor/torrc` e adicione a seguinte linha:
```torrc
HiddenServiceDir /var/lib/tor/nostr_server/
HiddenServicePort 80 127.0.0.1:3334
```
---
## Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
```bash
systemctl enable --now tor.service
```
O Tor irá gerar um endereço `.onion` para o seu servidor Nostr. Você pode encontrá-lo no arquivo `/var/lib/tor/nostr_server/hostname`.
---
## Observações ⚠️
- Com essa configuração, **os dados serão salvos no pendrive**, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço `.onion` do seu servidor Nostr será algo como: `ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion`.
---
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-

@ c582af78:698069cc
2025-02-13 01:04:26
# **The Nine Orders of Angels: A Guide to the Celestial Hierarchy**
When we think of angels, we often picture winged figures in flowing robes, guiding and protecting humanity. But the biblical and theological reality is far more complex—and often stranger—than these familiar depictions.
The word *angel* comes from the Greek *angelos*, meaning “messenger,” but in scripture, angels serve a wide range of roles beyond delivering divine messages. Some are warriors wielding swords and leading celestial armies, others uphold the very throne of God, and some appear as multi-winged, multi-eyed beings beyond human comprehension.
To bring order to this celestial realm, theologians—most notably Thomas Aquinas—classified angels into a hierarchy of **nine types**, divided into **three orders** based on their function and proximity to God.
- **The lowest order** interacts with humanity.
- **The middle order** governs spiritual and cosmic forces.
- **The highest order** exists solely to serve and glorify God.
Today, we explore these **nine ranks of angels**—from the familiar to the truly otherworldly.
---
## **I. The Third Order: Angels Who Interact with Humanity**
*(The lowest tier of angels, closest to humans, acting as messengers and protectors.)*
### **1. Angels – The Messengers**
https://image.nostr.build/b6462b67e14c8780896f465b664a521cdcdef7eb4b4314669b8d219aa36964c5.jpg
These are the angels most commonly associated with divine guidance. According to Aquinas, every person has a **guardian angel**—an unseen protector guiding them through life.
In *Genesis 28:12*, Jacob’s vision of a ladder stretching to Heaven shows angels ascending and descending, delivering messages and fulfilling divine commands. Some, like those who visited Abraham, even appeared as ordinary men, without wings or supernatural radiance.
### **2. Archangels – The Divine Enforcers**
https://image.nostr.build/af8799efb61c5a64e958450bcd5aee55d2cade931cfc5ca7f0ae8745ccd4c45a.jpg
Archangels carry out the most crucial missions in scripture. Gabriel announced the birth of Jesus to Mary, while Michael led the charge against Satan in the war for Heaven.
Though only **Michael** is explicitly called an archangel in the Bible, tradition assigns this title to others, including **Raphael** and **Uriel**. Archangels serve as warriors and heralds, executing God’s most urgent decrees.
### **3. Principalities – Guardians of Nations**
https://image.nostr.build/bc7cd78acb656be6c946da32244bfb9ecdfe9a7d1bd80e47eca764cae4a88b95.jpg
Principalities oversee nations, cities, and communities, influencing their spiritual well-being. While they are not explicitly named in scripture, *Colossians 1:16* references “thrones, dominions, principalities, and powers.”
Tradition suggests that Principalities guide earthly leaders, strengthening them in times of crisis—and perhaps even aiding biblical figures like King David in battle.
---
## **II. The Second Order: The Heavenly Governors**
*(These angels reside in Heaven but influence earthly affairs, ensuring divine order is maintained.)*
### **4. Powers – The Celestial Warriors**
https://image.nostr.build/1768abcbaefb2d1d21654a869b356d86a45d76a82197b9568528d4d4b9f0ef69.jpg
Powers act as Heaven’s **military defenders**, guarding the spiritual realm from demonic forces. They are often depicted in armor, wielding weapons as they engage in cosmic battles.
According to Christian tradition, Powers also **escort souls to Heaven**, ensuring their safe passage after death. Some believe that the battle between good and evil plays out, in part, through these celestial warriors.
### **5. Virtues – The Miracle Workers**
https://image.nostr.build/b9a1e52f1dd4ef0f7e7dd198d81e7cd171eede8a64a40cac8176e12a5419aeba.jpg
Virtues are associated with **miracles and nature**, regulating celestial phenomena and assisting in divine interventions.
In Christian tradition, the two angels present at **Christ’s Ascension** are often considered Virtues, manifesting God’s power on Earth.
### **6. Dominions – The Angelic Rulers**
https://image.nostr.build/0900d97bf545736e5edc1521f46a8afbf0e93fd81e472c88a56744ff0f56ce48.jpg
Dominions do not typically interact with humans directly. Instead, they act as **commanders**, overseeing lower angels and ensuring divine order is maintained.
They are described as serene, wise beings, often depicted holding golden staffs and orbs, symbolizing their authority and their close relationship with God.
---
## **III. The First Order: The Angels Closest to God**
*(These angels exist solely to worship and serve God, residing in the highest realms of Heaven.)*
### **7. Thrones – The Wheels of God’s Chariot**
https://image.nostr.build/d9f1e465129b138f4f960ee43ee9e06ceb3fd6f57e9658cd275e1ac1576b3c02.jpg
Among the most mysterious angelic beings, Thrones are described in *Ezekiel’s vision* as **wheels covered in eyes, spinning within wheels**:
> *“As I looked, I saw a wheel on the ground beside each creature with its four faces... Their rims were full of eyes all around. Wherever the spirit would go, they would go, because the spirit of the living creatures was in the wheels.”*
> — *Ezekiel 1:15-21*
Thrones serve as **God’s chariot**, supporting His throne and executing divine justice. Their strange, abstract form symbolizes stability and divine order.
### **8. Cherubim – The Guardians of Glory**
https://image.nostr.build/e921ad4c32f56ebbb8f1bcb1ca2bc6eed1c736ec896429e008fc5b71cf2fd151.jpg
Cherubim have been drastically misrepresented in art. Far from the **plump, childlike figures** seen in Renaissance paintings, the **biblical Cherubim** are **fearsome beings**.
In *Ezekiel 10*, they are described as having **four faces**—a man, a lion, an ox, and an eagle—along with **four wings**.
They also appear in *Genesis 3:24*, where they **guard the entrance to Eden with flaming swords** after Adam and Eve’s expulsion.
https://image.nostr.build/f51286d4f35d9d6e85d8559600188ecc89a0969c3985814cae56cd230ea5db00.jpg
Aquinas even suggested that **Satan himself was a fallen Cherub**. This theory is supported by *Ezekiel 28*, which describes an angelic being cast down from God’s presence:
> *“You were anointed as a guardian cherub... You were blameless in your ways until wickedness was found in you... So I drove you in disgrace from the mount of God, and I expelled you, guardian cherub.”*
> — *Ezekiel 28:14-17*
### **9. Seraphim – The Highest & Holiest**
Seraphim stand **at the very throne of God**, continuously worshiping Him.
In *Isaiah’s vision* (*Isaiah 6:1-7*), they are described as having **six wings**—two to fly, two to cover their feet, and two to cover their faces, symbolizing their humility before God. They sing:
> **“Holy, holy, holy is the Lord of hosts; the whole earth is full of His glory.”**
When Seraphim reappear in *Revelation*, their wings are now **covered in eyes**, representing divine omniscience. Their song shifts slightly:
> *“Holy, holy, holy is the Lord God Almighty, who was and is and is to come!”*
> — *Revelation 4:8*
https://image.nostr.build/3495ccf6c0ba26b42d3e2b438ec19232cca148f6fbf29e5edd4129f5a198d05b.jpg
Unlike other angelic beings, Seraphim do not interact with humans—they exist purely to **glorify God**.
---
## **“Be Not Afraid”**
The angelic hierarchy provides a glimpse into the vast celestial order governing God’s universe. From the lowest messengers to the highest divine worshippers, each angelic being plays a unique role in the unfolding story of creation and salvation.
Yet, despite their differences, there is one striking similarity across biblical encounters with angels:
They often begin with a single phrase—
**“Be not afraid.”**
-

@ b8851a06:9b120ba1
2025-01-14 15:28:32
## **It Begins with a Click**
It starts with a click: *“Do you agree to our terms and conditions?”*\
You scroll, you click, you comply. A harmless act, right? But what if every click was a surrender? What if every "yes" was another link in the chain binding you to a life where freedom requires approval?
This is the age of permission. Every aspect of your life is mediated by gatekeepers. Governments demand forms, corporations demand clicks, and algorithms demand obedience. You’re free, of course, as long as you play by the rules. But who writes the rules? Who decides what’s allowed? Who owns your life?
---
## **Welcome to Digital Serfdom**
We once imagined the internet as a digital frontier—a vast, open space where ideas could flow freely and innovation would know no bounds. But instead of creating a decentralized utopia, we built a new feudal system.
- Your data? Owned by the lords of Big Tech.
- Your money? Controlled by banks and bureaucrats who can freeze it on a whim.
- Your thoughts? Filtered by algorithms that reward conformity and punish dissent.
The modern internet is a land of serfs and lords, and guess who’s doing the farming? You. Every time you agree to the terms, accept the permissions, or let an algorithm decide for you, you till the fields of a system designed to control, not liberate.
They don’t call it control, of course. They call it *“protection.”* They say, “We’re keeping you safe,” as they build a cage so big you can’t see the bars.
---
## **Freedom in Chains**
But let’s be honest: we’re not just victims of this system—we’re participants. We’ve traded freedom for convenience, sovereignty for security. It’s easier to click “I Agree” than to read the fine print. It’s easier to let someone else hold your money than to take responsibility for it yourself. It’s easier to live a life of quiet compliance than to risk the chaos of true independence.
We tell ourselves it’s no big deal. What’s one click? What’s one form? But the permissions pile up. The chains grow heavier. And one day, you wake up and realize you’re free to do exactly what the system allows—and nothing more.
---
## **The Great Unpermissioning**
It doesn’t have to be this way. You don’t need their approval. You don’t need their systems. You don’t need their permission.
The Great Unpermissioning is not a movement—it’s a mindset. It’s the refusal to accept a life mediated by gatekeepers. It’s the quiet rebellion of saying, *“No.”* It’s the realization that the freedom you seek won’t be granted—it must be reclaimed.
- **Stop asking.** Permission is their tool. Refusal is your weapon.
- **Start building.** Embrace tools that decentralize power: Bitcoin, encryption, open-source software, decentralized communication. Build systems they can’t control.
- **Stand firm.** They’ll tell you it’s dangerous. They’ll call you a radical. But remember: the most dangerous thing you can do is comply.
The path won’t be easy. Freedom never is. But it will be worth it.
---
## **The New Frontier**
The age of permission has turned us into digital serfs, but there’s a new frontier on the horizon. It’s a world where you control your money, your data, your decisions. It’s a world of encryption, anonymity, and sovereignty. It’s a world built not on permission but on principles.
This world won’t be given to you. You have to build it. You have to fight for it. And it starts with one simple act: refusing to comply.
---
## **A Final Word**
They promised us safety, but what they delivered was submission. The age of permission has enslaved us to the mundane, the monitored, and the mediocre. The Great Unpermissioning isn’t about tearing down the old world—it’s about walking away from it.
You don’t need to wait for their approval. You don’t need to ask for their permission. The freedom you’re looking for is already yours. Permission is their power—refusal is yours.
-

@ c582af78:698069cc
2025-02-13 01:03:50
## **How to Be Happy: Aristotle’s Blueprint for a Flourishing Life**
Everyone wants happiness. The problem? Most people don’t actually know what happiness is.
Ask someone what would make them happy, and they’ll likely mention wealth, pleasure, success, or recognition. Over 2,000 years ago, Aristotle heard the same answers—and he rejected them.
According to Aristotle, happiness isn’t something you *have*, but something you *do*. True happiness—what he called *eudaimonia*—isn’t about fleeting pleasures or external rewards. It’s about living well, cultivating virtue, and engaging deeply in life’s highest pursuits.
So, what’s Aristotle’s formula for happiness? It comes down to three essential steps.
---
### **The False Paths to Happiness**
Aristotle observed that most people chase happiness in three common ways: **wealth, pleasure, and honor**. While each has its appeal, none can sustain true fulfillment.
Take **wealth**, for example. Money provides security and opportunity, but it doesn’t guarantee satisfaction. Aristotle noted that many people who seek wealth become obsessed with accumulating it rather than using it wisely. The result? An endless chase with no real contentment.
**Pleasure** is even trickier. Aristotle acknowledged that pleasure is a natural good, but he warned against making it life’s ultimate goal. Living only for pleasure leads to a cycle of chasing temporary highs without ever achieving deeper fulfillment. As Aristotle put it, this is the life of *“fatted cattle”*—comfortable, but lacking excellence.
Then there’s **honor**. Recognition feels good, but it depends on the approval of others. If you live solely for status, you risk valuing recognition over real achievement. Honor for its own sake is empty unless it’s tied to genuine virtue.
**Aristotle’s conclusion?** These paths don’t lead to true happiness. They are distractions, not destinations.
---
### **The True Meaning of Happiness**
If wealth, pleasure, and honor aren’t enough, then what *is* happiness?
To answer that, we need to understand Aristotle’s term *eudaimonia*. Unlike our modern idea of happiness as a feeling, *eudaimonia* means **flourishing**—a life of purpose, virtue, and excellence.
The key difference is that **wealth, pleasure, and honor are passive**—they happen *to* you. But *eudaimonia* is **active**—it’s something you cultivate through action.
In his *Nicomachean Ethics*, Aristotle defines happiness as *“the activity of the soul in accordance with virtue.”* It’s not a prize to be won, but a way of living.
A great example comes from sports. A skilled athlete doesn’t just sit around feeling happy—his joy comes from being *in motion*: training, competing, improving, and fully engaging in his craft.
For Aristotle, happiness works the same way. It comes from actively developing your best qualities, not passively indulging in comfort.
But how do you put this into practice?
---
## **Aristotle’s 3-Step Blueprint for a Good Life**
Aristotle’s guide to happiness is surprisingly practical. Here’s how to apply it:
### **1. Cultivate Virtue Through Habit**
Virtue isn’t something you’re born with—it’s something you practice.
Just as an athlete trains for competition, you develop virtue by repeatedly choosing good actions. Courage, patience, and wisdom don’t just appear; they become part of you through habit.
As Aristotle famously said:
> **“We are what we repeatedly do. Excellence, then, is not an act, but a habit.”**
Want to be generous? **Give more often.**
Want to be disciplined? **Practice restraint.**
Over time, these actions shape your character—and character shapes happiness.
### **2. Engage Fully in Meaningful Work**
Happiness isn’t found in passivity, but in action.
Aristotle believed that true fulfillment comes from using your talents to their fullest extent. This applies to everything from philosophy to craftsmanship to leadership. The key is **engagement**.
Think of the satisfaction a musician feels while playing at their best, or the pride of a craftsman perfecting their work. These moments—where skill, effort, and purpose align—are true happiness in action.
Contrary to popular belief, happiness isn’t about doing less. **It’s about doing the right things, with full commitment.**
### **3. Seek the Right Kind of Pleasure**
Aristotle didn’t reject pleasure—he just emphasized choosing the *right* kind.
Lower pleasures—like eating, drinking, or binge-watching TV—may feel good in the moment but often leave you feeling empty afterward. Higher pleasures—such as learning, mastering a craft, or cultivating meaningful relationships—lead to lasting fulfillment.
The goal isn’t to reject pleasure, but to **align it with virtue**. Instead of chasing immediate gratification, seek pleasures that contribute to long-term flourishing.
---
## **Happiness as a Way of Life**
It’s important to understand that happiness isn’t a destination—it’s a **practice**. It’s something cultivated daily by engaging in meaningful work, growing in virtue, and living with purpose.
But most importantly, **happiness isn’t about what happens to you—it’s about who you become**.
By cultivating *eudaimonia*, you change the essence of your being—just as a farmer who nurtures his crops becomes stronger through his labor.
True happiness isn’t a fleeting emotion, but the natural result of a life well lived. The more you nurture virtue through action, the more deeply happiness takes root—until it becomes not just something you seek, but something you embody.
-

@ 6389be64:ef439d32
2025-01-14 01:31:12
Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
# Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
# Meet The Forest Walker

For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
# The Small Branch Chipper

When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
# The Gassifier

The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
# Biochar: The Waste

Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
# Wood Vinegar: More Waste

Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
# The Internal Combustion Engine

Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
# CO2 Production For Growth

Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
# The Branch Drones

During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
# The Bitcoin Miner

Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
# The Mesh Network

What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
# Back To The Chain

Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
# Sensor Packages
### LiDaR

The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
### pH, Soil Moisture, and Cation Exchange Sensing

The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
### Weather Data

Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
# Noise Suppression

Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
# Fire Safety

A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
# The Wrap

How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-

@ 57d1a264:69f1fee1
2025-02-13 00:28:45
This past week, @erik_ and @Sushant have been working on improving the onboarding flow for [Sovran](https://sovranbitcoin.com/) bitcoin wallet. First revision on thee figma file below, would appreciate any feedback.


https://www.figma.com/design/inNLo6AaPMX26D3GumcXGC/UI%2FUX-Audit--Onboarding-User-Flow?node-id=0-1&t=Wl0EVhH5fJgYYSJI-1
If you want to review the UX audit of the current flow, see the feedback provided, and check Sushant's initial suggestions, you can do so here:

https://www.figma.com/board/Jfo4nLIKyR6lacokXze4Mv/Sovran-Onboarding-UX-Audit?node-id=0-1&t=gOZyo57zfeqxFXeB-1
originally posted at https://stacker.news/items/884272
-

@ e3ba5e1a:5e433365
2025-01-13 16:47:27
My blog posts and reading material have both been on a decidedly economics-heavy slant recently. The topic today, incentives, squarely falls into the category of economics. However, when I say economics, I’m not talking about “analyzing supply and demand curves.” I’m talking about the true basis of economics: understanding how human beings make decisions in a world of scarcity.
A fair definition of incentive is “a reward or punishment that motivates behavior to achieve a desired outcome.” When most people think about economic incentives, they’re thinking of money. If I offer my son $5 if he washes the dishes, I’m incentivizing certain behavior. We can’t guarantee that he’ll do what I want him to do, but we can agree that the incentive structure itself will guide and ultimately determine what outcome will occur.
The great thing about monetary incentives is how easy they are to talk about and compare. “Would I rather make $5 washing the dishes or $10 cleaning the gutters?” But much of the world is incentivized in non-monetary ways too. For example, using the “punishment” half of the definition above, I might threaten my son with losing Nintendo Switch access if he doesn’t wash the dishes. No money is involved, but I’m still incentivizing behavior.
And there are plenty of incentives beyond our direct control\! My son is *also* incentivized to not wash dishes because it’s boring, or because he has some friends over that he wants to hang out with, or dozens of other things. Ultimately, the conflicting array of different incentive structures placed on him will ultimately determine what actions he chooses to take.
## Why incentives matter
A phrase I see often in discussions—whether they are political, parenting, economic, or business—is “if they could **just** do…” Each time I see that phrase, I cringe a bit internally. Usually, the underlying assumption of the statement is “if people would behave contrary to their incentivized behavior then things would be better.” For example:
* If my kids would just go to bed when I tell them, they wouldn’t be so cranky in the morning.
* If people would just use the recycling bin, we wouldn’t have such a landfill problem.
* If people would just stop being lazy, our team would deliver our project on time.
In all these cases, the speakers are seemingly flummoxed as to why the people in question don’t behave more rationally. The problem is: each group is behaving perfectly rationally.
* The kids have a high time preference, and care more about the joy of staying up now than the crankiness in the morning. Plus, they don’t really suffer the consequences of morning crankiness, their parents do.
* No individual suffers much from their individual contribution to a landfill. If they stopped growing the size of the landfill, it would make an insignificant difference versus the amount of effort they need to engage in to properly recycle.
* If a team doesn’t properly account for the productivity of individuals on a project, each individual receives less harm from their own inaction. Sure, the project may be delayed, company revenue may be down, and they may even risk losing their job when the company goes out of business. But their laziness individually won’t determine the entirety of that outcome. By contrast, they greatly benefit from being lazy by getting to relax at work, go on social media, read a book, or do whatever else they do when they’re supposed to be working.

My point here is that, as long as you ignore the reality of how incentives drive human behavior, you’ll fail at getting the outcomes you want.
If everything I wrote up until now made perfect sense, you understand the premise of this blog post. The rest of it will focus on a bunch of real-world examples to hammer home the point, and demonstrate how versatile this mental model is.
## Running a company
Let’s say I run my own company, with myself as the only employee. My personal revenue will be 100% determined by my own actions. If I decide to take Tuesday afternoon off and go fishing, I’ve chosen to lose that afternoon’s revenue. Implicitly, I’ve decided that the enjoyment I get from an afternoon of fishing is greater than the potential revenue. You may think I’m being lazy, but it’s my decision to make. In this situation, the incentive–money–is perfectly aligned with my actions.
Compare this to a typical company/employee relationship. I might have a bank of Paid Time Off (PTO) days, in which case once again my incentives are relatively aligned. I know that I can take off 15 days throughout the year, and I’ve chosen to use half a day for the fishing trip. All is still good.
What about unlimited time off? Suddenly incentives are starting to misalign. I don’t directly pay a price for not showing up to work on Tuesday. Or Wednesday as well, for that matter. I might ultimately be fired for not doing my job, but that will take longer to work its way through the system than simply not making any money for the day taken off.
Compensation overall falls into this misaligned incentive structure. Let’s forget about taking time off. Instead, I work full time on a software project I’m assigned. But instead of using the normal toolchain we’re all used to at work, I play around with a new programming language. I get the fun and joy of playing with new technology, and potentially get to pad my resume a bit when I’m ready to look for a new job. But my current company gets slower results, less productivity, and is forced to subsidize my extracurricular learning.
When a CEO has a bonus structure based on profitability, he’ll do everything he can to make the company profitable. This might include things that actually benefit the company, like improving product quality, reducing internal red tape, or finding cheaper vendors. But it might also include destructive practices, like slashing the R\&D budget to show massive profits this year, in exchange for a catastrophe next year when the next version of the product fails to ship.

Or my favorite example. My parents owned a business when I was growing up. They had a back office where they ran operations like accounting. All of the furniture was old couches from our house. After all, any money they spent on furniture came right out of their paychecks\! But in a large corporate environment, each department is generally given a budget for office furniture, a budget which doesn’t roll over year-to-year. The result? Executives make sure to spend the entire budget each year, often buying furniture far more expensive than they would choose if it was their own money.
There are plenty of details you can quibble with above. It’s in a company’s best interest to give people downtime so that they can come back recharged. Having good ergonomic furniture can in fact increase productivity in excess of the money spent on it. But overall, the picture is pretty clear: in large corporate structures, you’re guaranteed to have mismatches between the company’s goals and the incentive structure placed on individuals.
Using our model from above, we can lament how lazy, greedy, and unethical the employees are for doing what they’re incentivized to do instead of what’s right. But that’s simply ignoring the reality of human nature.
# Moral hazard
Moral hazard is a situation where one party is incentivized to take on more risk because another party will bear the consequences. Suppose I tell my son when he turns 21 (or whatever legal gambling age is) that I’ll cover all his losses for a day at the casino, but he gets to keep all the winnings.
What do you think he’s going to do? The most logical course of action is to place the largest possible bets for as long as possible, asking me to cover each time he loses, and taking money off the table and into his bank account each time he wins.

But let’s look at a slightly more nuanced example. I go to a bathroom in the mall. As I’m leaving, I wash my hands. It will take me an extra 1 second to turn off the water when I’m done washing. That’s a trivial price to pay. If I *don’t* turn off the water, the mall will have to pay for many liters of wasted water, benefiting no one. But I won’t suffer any consequences at all.
This is also a moral hazard, but most people will still turn off the water. Why? Usually due to some combination of other reasons such as:
1. We’re so habituated to turning off the water that we don’t even consider *not* turning it off. Put differently, the mental effort needed to not turn off the water is more expensive than the 1 second of time to turn it off.
2. Many of us have been brought up with a deep guilt about wasting resources like water. We have an internal incentive structure that makes the 1 second to turn off the water much less costly than the mental anguish of the waste we created.
3. We’re afraid we’ll be caught by someone else and face some kind of social repercussions. (Or maybe more than social. Are you sure there isn’t a law against leaving the water tap on?)
Even with all that in place, you may notice that many public bathrooms use automatic water dispensers. Sure, there’s a sanitation reason for that, but it’s also to avoid this moral hazard.
A common denominator in both of these is that the person taking the action that causes the liability (either the gambling or leaving the water on) is not the person who bears the responsibility for that liability (the father or the mall owner). Generally speaking, the closer together the person making the decision and the person incurring the liability are, the smaller the moral hazard.
It’s easy to demonstrate that by extending the casino example a bit. I said it was the father who was covering the losses of the gambler. Many children (though not all) would want to avoid totally bankrupting their parents, or at least financially hurting them. Instead, imagine that someone from the IRS shows up at your door, hands you a credit card, and tells you you can use it at a casino all day, taking home all the chips you want. The money is coming from the government. How many people would put any restriction on how much they spend?
And since we’re talking about the government already…
## Government moral hazards
As I was preparing to write this blog post, the California wildfires hit. The discussions around those wildfires gave a *huge* number of examples of moral hazards. I decided to cherry-pick a few for this post.
The first and most obvious one: California is asking for disaster relief funds from the federal government. That sounds wonderful. These fires were a natural disaster, so why shouldn’t the federal government pitch in and help take care of people?
The problem is, once again, a moral hazard. In the case of the wildfires, California and Los Angeles both had ample actions they could have taken to mitigate the destruction of this fire: better forest management, larger fire department, keeping the water reservoirs filled, and probably much more that hasn’t come to light yet.
If the federal government bails out California, it will be a clear message for the future: your mistakes will be fixed by others. You know what kind of behavior that incentivizes? More risky behavior\! Why spend state funds on forest management and extra firefighters—activities that don’t win politicians a lot of votes in general—when you could instead spend it on a football stadium, higher unemployment payments, or anything else, and then let the feds cover the cost of screw-ups.
You may notice that this is virtually identical to the 2008 “too big to fail” bail-outs. Wall Street took insanely risky behavior, reaped huge profits for years, and when they eventually got caught with their pants down, the rest of us bailed them out. “Privatizing profits, socializing losses.”

And here’s the absolute best part of this: I can’t even truly blame either California *or* Wall Street. (I mean, I *do* blame them, I think their behavior is reprehensible, but you’ll see what I mean.) In a world where the rules of the game implicitly include the bail-out mentality, you would be harming your citizens/shareholders/investors if you didn’t engage in that risky behavior. Since everyone is on the hook for those socialized losses, your best bet is to maximize those privatized profits.
There’s a lot more to government and moral hazard, but I think these two cases demonstrate the crux pretty solidly. But let’s leave moral hazard behind for a bit and get to general incentivization discussions.
# Non-monetary competition
At least 50% of the economics knowledge I have comes from the very first econ course I took in college. That professor was amazing, and had some very colorful stories. I can’t vouch for the veracity of the two I’m about to share, but they definitely drive the point home.
In the 1970s, the US had an oil shortage. To “fix” this problem, they instituted price caps on gasoline, which of course resulted in insufficient gasoline. To “fix” this problem, they instituted policies where, depending on your license plate number, you could only fill up gas on certain days of the week. (Irrelevant detail for our point here, but this just resulted in people filling up their tanks more often, no reduction in gas usage.)
Anyway, my professor’s wife had a friend. My professor described in *great* detail how attractive this woman was. I’ll skip those details here since this is a PG-rated blog. In any event, she never had any trouble filling up her gas tank any day of the week. She would drive up, be told she couldn’t fill up gas today, bat her eyes at the attendant, explain how helpless she was, and was always allowed to fill up gas.
This is a demonstration of *non-monetary compensation*. Most of the time in a free market, capitalist economy, people are compensated through money. When price caps come into play, there’s a limit to how much monetary compensation someone can receive. And in that case, people find other ways of competing. Like this woman’s case: through using flirtatious behavior to compensate the gas station workers to let her cheat the rules.
The other example was much more insidious. Santa Monica had a problem: it was predominantly wealthy and white. They wanted to fix this problem, and decided to put in place rent controls. After some time, they discovered that Santa Monica had become *wealthier and whiter*, the exact opposite of their desired outcome. Why would that happen?
Someone investigated, and ended up interviewing a landlady that demonstrated the reason. She was an older white woman, and admittedly racist. Prior to the rent controls, she would list her apartments in the newspaper, and would be legally obligated to rent to anyone who could afford it. Once rent controls were in place, she took a different tact. She knew that she would only get a certain amount for the apartment, and that the demand for apartments was higher than the supply. That meant she could be picky.
She ended up finding tenants through friends-of-friends. Since it wasn’t an official advertisement, she wasn’t legally required to rent it out if someone could afford to pay. Instead, she got to interview people individually and then make them an offer. Normally, that would have resulted in receiving a lower rental price, but not under rent controls.
So who did she choose? A young, unmarried, wealthy, white woman. It made perfect sense. Women were less intimidating and more likely to maintain the apartment better. Wealthy people, she determined, would be better tenants. (I have no idea if this is true in practice or not, I’m not a landlord myself.) Unmarried, because no kids running around meant less damage to the property. And, of course, white. Because she was racist, and her incentive structure made her prefer whites.
You can deride her for being racist, I won’t disagree with you. But it’s simply the reality. Under the non-rent-control scenario, her profit motive for money outweighed her racism motive. But under rent control, the monetary competition was removed, and she was free to play into her racist tendencies without facing any negative consequences.
## Bureaucracy
These were the two examples I remember for that course. But non-monetary compensation pops up in many more places. One highly pertinent example is bureaucracies. Imagine you have a government office, or a large corporation’s acquisition department, or the team that apportions grants at a university. In all these cases, you have a group of people making decisions about handing out money that has no monetary impact on them. If they give to the best qualified recipients, they receive no raises. If they spend the money recklessly on frivolous projects, they face no consequences.
Under such an incentivization scheme, there’s little to encourage the bureaucrats to make intelligent funding decisions. Instead, they’ll be incentivized to spend the money where they recognize non-monetary benefits. This is why it’s so common to hear about expensive meals, gift bags at conferences, and even more inappropriate ways of trying to curry favor with those that hold the purse strings.
Compare that ever so briefly with the purchases made by a small mom-and-pop store like my parents owned. Could my dad take a bribe to buy from a vendor who’s ripping him off? Absolutely he could\! But he’d lose more on the deal than he’d make on the bribe, since he’s directly incentivized by the deal itself. It would make much more sense for him to go with the better vendor, save $5,000 on the deal, and then treat himself to a lavish $400 meal to celebrate.
# Government incentivized behavior
This post is getting longer in the tooth than I’d intended, so I’ll finish off with this section and make it a bit briefer. Beyond all the methods mentioned above, government has another mechanism for modifying behavior: through directly changing incentives via legislation, regulation, and monetary policy. Let’s see some examples:
* Artificial modification of interest rates encourages people to take on more debt than they would in a free capital market, leading to [malinvestment](https://en.wikipedia.org/wiki/Malinvestment) and a consumer debt crisis, and causing the boom-bust cycle we all painfully experience.
* Going along with that, giving tax breaks on interest payments further artificially incentivizes people to take on debt that they wouldn’t otherwise.
* During COVID-19, at some points unemployment benefits were greater than minimum wage, incentivizing people to rather stay home and not work than get a job, leading to reduced overall productivity in the economy and more printed dollars for benefits. In other words, it was a perfect recipe for inflation.
* The tax code gives deductions to “help” people. That might be true, but the real impact is incentivizing people to make decisions they wouldn’t have otherwise. For example, giving out tax deductions on children encourages having more kids. Tax deductions on childcare and preschools incentivizes dual-income households. Whether or not you like the outcomes, it’s clear that it’s government that’s encouraging these outcomes to happen.
* Tax incentives cause people to engage in behavior they wouldn’t otherwise (daycare+working mother, for example).
* Inflation means that the value of your money goes down over time, which encourages people to spend more today, when their money has a larger impact. (Milton Friedman described this as [high living](https://www.youtube.com/watch?v=ZwNDd2_beTU).)
# Conclusion
The idea here is simple, and fully encapsulated in the title: incentives determine outcomes. If you want to know how to get a certain outcome from others, incentivize them to want that to happen. If you want to understand why people act in seemingly irrational ways, check their incentives. If you’re confused why leaders (and especially politicians) seem to engage in destructive behavior, check their incentives.
We can bemoan these realities all we want, but they *are* realities. While there are some people who have a solid internal moral and ethical code, and that internal code incentivizes them to behave against their externally-incentivized interests, those people are rare. And frankly, those people are self-defeating. People *should* take advantage of the incentives around them. Because if they don’t, someone else will.
(If you want a literary example of that last comment, see the horse in Animal Farm.)
How do we improve the world under these conditions? Make sure the incentives align well with the overall goals of society. To me, it’s a simple formula:
* Focus on free trade, value for value, as the basis of a society. In that system, people are always incentivized to provide value to other people.
* Reduce the size of bureaucracies and large groups of all kinds. The larger an organization becomes, the farther the consequences of decisions are from those who make them.
* And since the nature of human beings will be to try and create areas where they can control the incentive systems to their own benefits, make that as difficult as possible. That comes in the form of strict limits on government power, for example.
And even if you don’t want to buy in to this conclusion, I hope the rest of the content was educational, and maybe a bit entertaining\!
-

@ 5579d5c0:db104ded
2025-02-12 23:41:09
Most people think their metabolism is "broken" because they can't lose weight, feel sluggish, or gain fat easily.
The truth? **Your metabolism isn’t broken, it’s just out of sync.**
Your body doesn’t just burn calories randomly.
It follows a natural **24-hour rhythm**, dictated by light exposure, movement, meal timing, and sleep.
When these cues are off, your metabolism becomes dysfunctional.
The good news?
You don’t need to diet harder or exercise more.
**You need to realign your metabolism with your body’s natural rhythm.**
---
### Why your metabolism feels “broken”
Your body is designed to run on **timing signals, when to eat, when to move, when to rest**. Modern life disrupts these natural rhythms, leading to:
**→ Low energy & afternoon crashes**: Skipping morning sunlight and staying indoors all day.
**→ Stubborn belly fat & slow fat loss**: Eating at the wrong times, late-night snacking, and chronic stress.
**→ Constant cravings & hunger:** Poor meal timing and eating foods that spike blood sugar too often.
**→ Poor sleep & recovery**: Late night screen use, artificial light, and erratic bedtimes.
The problem **isn’t your metabolism, it’s your environment and habits.**
---
### How to reset your metabolism naturally
You don’t need extreme diets, calorie counting, or hours in the gym.
Instead, **align your metabolism with your body’s natural timing signals** by focusing on these fundamentals:
### 1. Get natural light first thing in the morning
Light in the first 30 minutes after waking sets your circadian rhythm (body clock), kickstarts hormone production, and improves insulin sensitivity.
This simple habit helps to regulate hunger, energy, and fat-burning.
**Action step:** Step outside for at least 5–10 minutes within 30 minutes of waking, no sunglasses, no contacts, only natural light exposure and take regular outdoor breaks during the day.
---
### 2. Stop eating late at night
Eating late, especially high-carb/high-fat meals, signals your body to store fat instead of burning it.
Late-night eating also disrupts sleep, which further impairs fat loss.
**Action step:** Keep meals within a **10-12 hour eating window**, preferably between sunrise and sunset. **No snacking**. Finish your last meal **at least 3 hours before bed**.
---
### 3. Move throughout the day (Not just at the gym)
Your metabolism isn’t just about burning calories, it’s about **how efficiently your body uses energy**.
Sitting for long hours disrupts metabolic function, even if you work out later.
**Action step:** Take a **5-minute movement break** every 1–2 hours. Stand, stretch, or better still go for a quick walk outside.
---
### 4. Prioritise deep, uninterrupted sleep
Your body **burns fat and repairs muscle while you sleep**.
Poor sleep increases hunger hormones (Ghrelin), prevents Leptin from working properly, and makes you crave junk food the next day.
**Action step:** Dim lights after sunset, wear blue light blocking glasses, avoid screens 30-60 minutes before bed, and aim for **7.5-9 hours of quality sleep**.
---
### 5. Eat nutrient-dense foods
What you eat matters, but **when** you eat it matters just as much.
Front-loading protein and nutrients earlier in the day supports fat-burning and stabilises energy.
**Action step:** Eat a **high-protein, nutrient-dense breakfast** and **avoid refined carbs & sugar, especially in the morning,** to prevent cravings later.
---
Your metabolism isn’t broken, it’s just out of sync.
Instead of obsessing over calories, **focus on realigning your body with its natural rhythms**:
→ **Morning sunlight** to set your metabolism for the day.
→ **Aligned meal timing** by eating during daylight & avoiding late-night eating.
→ **Frequent movement** to prevents metabolic slowdown from sitting.
→ **Quality sleep** which regulates fat-burning and hunger hormones.
→ **Nutrient-dense eating** giving your body what it needs.
Fix your metabolism without dieting harder, just live in sync with how your body is designed to function.
\-Chris
---
If you want a simple methodical approach to fixing your metabolism, Let’s talk.
**Book a free call here:** [**https://calendly.com/hello-chrispatrick**](https://calendly.com/hello-chrispatrick)
**Follow me on Nostr**: [**https://primal.net/chrispatrick**](https://primal.net/chrispatrick) or
[***nostr:npub124uatsq6pv74trzwvt34y4sx2z0uflhse7tkrv0pl69e8kcsfhkse30zsu***](https://primal.net/chrispatrick/npub124uatsq6pv74trzwvt34y4sx2z0uflhse7tkrv0pl69e8kcsfhkse30zsu)
-

@ 0d97beae:c5274a14
2025-01-11 16:52:08
This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs
## The reason why we have broken money
Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world.
In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes.
However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore.
Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too.
Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it.
## Bitcoin overcomes the "transfer of hard money" problem
Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design.
Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it.
Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive.
Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold.
## Bitcoin blurs the line between commodity and technology
Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules.
At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable.
Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases.
## The dangers of derivatives
A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold.
In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin.
Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense.
## Learn for yourself
If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody".
There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
-

@ 3b7fc823:e194354f
2025-02-12 23:13:57
**Staying Digitally Safe in Airports: A Comprehensive Guide**
Airports are hubs of activity, but they’re also places where your digital security can be at risk. From public Wi-Fi to potential device thefts, staying safe while traveling can feel overwhelming. However, with the right knowledge and precautions, you can protect yourself and enjoy your journey stress-free. Let’s dive into how to stay digitally safe in airports while traveling.
---
### **Understanding the Risks**
1. **Public Wi-Fi Vulnerabilities:**
- Airports often offer free Wi-Fi, but these networks can be unsecured or insecure. Hackers may use these networks to intercept sensitive data.
- Avoid using public Wi-Fi for personal banking, shopping, or handling sensitive information.
2. **Device Theft:**
- High-traffic areas like security checkpoints, gates, and lounges are hotspots for device thefts. Always keep your devices in secure locations, such as carry-on bags or locked briefcases.
3. **Malware and Phishing Attacks:**
- Some airports may have phishing attempts or malware distributed via pop-ups, email, or malicious websites.
4. **Physical Surveillance:**
- In some cases, law enforcement or security personnel may monitor your activities. Always be mindful of your surroundings to avoid unintended data exposure.
---
### **Best Practices for Staying Digitally Safe in Airports**
1. **Use a VPN for Extra Security:**
- Even secure airport Wi-Fi can expose your data if not encrypted. Use a reputable Virtual Private Network (VPN) to encrypt your internet traffic and protect your privacy.
- Always ensure your VPN is active when using public Wi-Fi.
2. **Minimize Sensitive Data on Public Devices:**
- Avoid carrying devices with sensitive information like passwords, credit card details, or personal identification numbers (PIIs).
3. **Encrypt Your Data:**
- Enable encryption for all your devices to protect data stored locally or in the cloud. Ensure your operating system and apps are updated with the latest security patches.
4. **Secure Your Devices:**
- Use cable locks or secure cases to lock down laptops, tablets, and smartphones when not in use.
- Remove screensavers that display your device passcode to prevent unauthorized access.
5. **Keep Antivirus Software Updated:**
- Install and maintain up-to-date antivirus software on all devices. This helps detect and remove malicious software (malware) that may be installed through compromised networks or phishing attempts.
6. **Avoid Plugging Into Public USB charging stations:**
- Refrain from using public USB ports or charging stations unless you know they’re secure. Malware can spread via these points.
7. **Use Caution With Lost and Found:**
- If you find a device or drop one accidentally, avoid using lost and found kiosks to pick it up. Instead, contact airport security for assistance in safely retrieving your property without exposing it to potential thieves.
8. **Stay Alert to Security Alerts:**
- Pay attention to announcements over the airport’s PA system regarding suspicious activity or security alerts. Follow any instructions provided by airport staff.
9. **Monitor Your Accounts Remotely:**
- If you suspect something is wrong (e.g., unusual transactions on your credit card), check your financial accounts immediately upon arriving at your destination. Notify your bank of potential fraudulent activity and report it to the authorities if necessary.
---
### **Additional Tips for Airport Safety**
1. **Use a Portable Power Bank:**
- Keep your devices charged so you don’t rely on public charging stations, which may be compromised.
2. **Travel with Backup Devices:**
- Always bring an extra SIM card, USB drive, or cloud storage to backup important data. This ensures you can access critical information even if your primary device is lost or damaged.
3. **Avoid Sharing Personal Information Over Earphone Rentals:**
- Refrain from using earphones rented from airport kiosks that may record or intercept your conversations. Stick to your own headphones or those provided by the airline.
4. **Use Airport Lounges Wisely:**
- If you’re using an airline lounge, avoid discussing sensitive information in public areas where it could be overheard.
5. **Keep Your Luggage in Sight:**
- Never leave your checked luggage unattended, as it may contain devices or documents with sensitive information.
6. **Plan for Data Loss:**
- Before leaving home, make a backup of all important files and photos on an external drive or cloud storage. This way, you can restore them if something goes wrong during your trip.
---
### **What to Do If Something Goes Wrong**
1. **Report Suspected Security Incidents:**
- If you notice unusual activity on your devices or suspect a security breach, inform airport security immediately.
2. **Contact Your Financial Institutions:**
- If you believe your financial information has been compromised, contact your bank or credit card provider to freeze your account and monitor for fraudulent charges.
3. **File a Police Report:**
- In cases of theft or suspected unauthorized access, file a report with local authorities and provide evidence (if available).
4. **Use Travel Insurance:**
- Check if your travel insurance covers theft, fraud, or data breaches. Submit a claim if you’re covered.
---
### **Extra Security Measures forTech-Savvy Travelers**
- **Two-Factor Authentication (2FA):** Enable 2FA for all your critical accounts before leaving home.
- **Biometric Locks:** Use biometric locks on your devices to add an extra layer of security.
- **Incident Response Plan:** Create a plan in advance for what to do if your devices are lost or compromised.
---
### **Final Tips**
- Always prioritize secure practices, even in seemingly safe environments like airports.
- Travel light but keep your important documents and devices close at hand.
- Remember that staying digitally safe is just as important as physical safety during your travels.
By following these tips, you can enjoy your trip with peace of mind, knowing your data and devices are protected. Happy traveling!
---
Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero
82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
-

@ 000002de:c05780a7
2025-02-12 22:41:17
The absolute embarrassment the Chiefs were subjected to... is the end of the their dominance? Of course they have a ton of talent and will win and maybe get back the Super Bowl this game really exposed them.
Its one thing to lose to a great team like the Eagles. Its another to be destroyed so fully. When I think about this game its not just on one person. Its coaching and players. I'm just wondering about the impact on the league watching this. Anyone who has played sports knows that a ton of it is mental. Teams can defeat themselves mentally. Does this defeat tell the league, yeah they aren't that good.
What do you think?
Edit: When I say "done", I mean the dynasty. I don't mean they are gonna have a losing record next year.
originally posted at https://stacker.news/items/884169
-

@ 000002de:c05780a7
2025-02-12 22:25:06
Honest question. I think he's a great TE but... haven't watched him a ton. I get a feeling he's overrated. Maybe not though. I watched him during the big game and was kinda surprised by his lack luster performance. He really seemed different to me.
Since then I've seen video of him not blocking for his QB and not really playing hard. Like he gave up. Does he really have a rep of not blocking? He looks pretty terrible on film. Now, I know I'm a Kittle fan and he is famously great at blocking and takes pride in it. Maybe I'm just using Kittle as the ruler and maybe that's not fair.
Also, I loved watching KC get destroyed so factor that in :)
originally posted at https://stacker.news/items/884156
-

@ 37fe9853:bcd1b039
2025-01-11 15:04:40
yoyoaa
-

@ 9673b322:1b75ee9e
2025-02-12 21:50:25
This is my test document for nostr publish
Although Sainsbury's was already in the midst of a plan to save £1bn over the next few years, the rise in employer's National Insurance contributions set out in the Budget has also been a factor in this latest restructuring plan.
### Add some text
this is is a test

-

@ 5d4b6c8d:8a1c1ee3
2025-02-12 18:36:48
Going off of memory, because I forgot to do this in the morning.
The last thing I ate were Costco samples yesterday afternoon and then I didn't eat again until lunch today. I'm pretty sure those two things were about 20 hours apart.
## Score Card
Day 1: 14 hour fast (13 dry)
Day 2: 15 hour fast (14 dry)
Day 3: 17 hours (16 dry)
Day 4: 18 hours (17 dry)
Day 5: 18 hours (16 dry)
Day 6: 19 hours (16 dry)
Day 7: 16 hours (15 dry)
Day 8: 18 hours (17 dry)
Day 9: 17 hours (17 dry)
Day 10: 15 hours (13 dry)
Day 11: 20 hours (19 dry)
Day 12: 20 hours (17 dry)
This winter storm is going to make getting my steps in a pain, but there's no way I'm letting myself lose the sats that I staked on the challenge.
originally posted at https://stacker.news/items/884000
-

@ 2e8970de:63345c7a
2025-02-12 17:50:27
originally posted at https://stacker.news/items/883959
-

@ 62033ff8:e4471203
2025-01-11 15:00:24
收录的内容中 kind=1的部分,实话说 质量不高。
所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。
所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。
而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。
https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。
我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。
我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛
幸运的是npub.pro 建站这样的,我觉得有点意思。
yakihonne 智能widget 也有意思
我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。
-

@ 4506e04e:8c16ba04
2025-01-10 13:26:46
The healthcare system, in its current state, is fundamentally broken. Under the fiat standard, big pharma exploits the sick in much the same way that banks and financial corporations drain economic power from individuals and small businesses. Despite massive investments, healthcare remains plagued by inefficiencies, inequities, and vulnerabilities. With rapidly aging population and low birth rates the access to healthcare is becoming more and more difficult and the system will break within the next couple of decades. Here are some of the major issues:
### Financial Drain with Minimal Returns
No matter how much money is poured into healthcare, it’s never enough. Administrative overheads, inflated costs, and inefficiencies ensure that resources are wasted instead of improving patient outcomes.
### Big Pharma’s Perverse Incentives
Pharmaceutical companies prioritize profit over cures. The system is designed to keep patients alive but perpetually dependent on treatments, rather than focusing on true cures.
### Administrative Bloat
The excessive overhead costs in administration siphon funds away from actual patient care.
### Fragmented Patient Records
There is no single global standard for managing and accessing healthcare records, creating inefficiencies and potential for errors.
### Cybersecurity Risks
Centralized healthcare systems are vulnerable to ransomware attacks, which can compromise patient safety and even pose threats to international security. For hospitals, such attacks are literally matters of life and death.
### Increasing Costs and Reduced Accessibility
Instead of becoming cheaper and more accessible, healthcare is growing more expensive and difficult to obtain, exacerbating inequities, yet nurses are one of the groups that's most underpaid!
## A Decentralized Solution
The solution lies in leveraging decentralization, encryption, and open-source technologies to transform the healthcare system. Thanks to innovations like Bitcoin and the Nostr protocol we now have the means to:
- **Empower Patients and Doctors:** Decentralized systems can give patients control over their medical data while reducing administrative costs for healthcare providers.
- **Enhance Security:** Encryption ensures data is secure, even in the face of cyber threats.
- **Improve Accessibility and Efficiency:** Open-source tools (like [Keycast](https://github.com/erskingardner/keycast)) can lower costs and provide customizable solutions tailored to specific healthcare needs.
note1327htu9gr327h38yu5f6tueye4cajp3kc69cs3gl7w6q6rz09ufqukl74j
## How Nostr Can Transform Healthcare
Nostr, short for “*Notes and Other Stuff Transmitted by Relays,*” is a decentralized protocol originally designed for communication but holds tremendous potential for industries such as healthcare. Its client-relay model allows patients and doctors to interact securely without relying on centralized servers. Here’s how it could work in a healthcare context:
### Decentralized Data Control:
Patients’ medical records can be securely stored and accessed via relays. Each patient’s identity is tied to a cryptographic public key, ensuring that they have full control over their data.
Doctors can access necessary records by connecting to relays the patient authorizes, ensuring data remains private and secure.
### Privacy Without Bureaucracy:
Nostr eliminates the need for cumbersome identity verification processes (e.g., KYC). Patients retain privacy without needing emails, IDs, or other personal identifiers.
### Customizable Access:
Patients can specify which doctors or healthcare providers can access their records by granting permissions via cryptographic signatures. These permissions can be adjusted or revoked at any time.
### Secure and Verifiable Communication:
All interactions between patients and doctors are signed with private keys, ensuring authenticity and preventing tampering.
Relays do not own or manipulate the data; they simply transmit it between authorized users.
### Resilient and Flexible Network:
Patients and doctors can choose which relays to use, and data can be published to multiple relays for redundancy. This ensures continuity of care even if a specific relay goes offline.
### Patient-Centric Data Ownership:
In the Nostr model, patients own their data. They can share it, manage it, or restrict access as they see fit, empowering them to take control of their health information.
### Enhanced Telemedicine:
Secure, encrypted communication enables remote consultations where doctors can access up-to-date patient records in real-time, providing better care.
By combining Nostr’s decentralized approach with healthcare-specific adaptations, this protocol can make the healthcare system more secure, efficient, and patient-focused.
## Meet Keycast
Keycast is a self-hosted open-source tool designed for secure and efficient private key management that can be applied to manage teams and policies. Its features can empower collaboration from micro-level ops like sharing access to one Nostr account to organising healthcare in the following ways:
1. **Team Management**:
- Organize users into teams representing departments or specialties (different policies).
- Streamline workflows by aligning permissions with roles.
2. **Granular Permissions**:
- Assign specific access rights to doctors, nurses, and administrative staff.
- Create layered permissions for actions such as accessing records, adding notes, or authorizing tests.
3. **Secure Key Management**:
- Encrypt and securely store keys locally, ensuring data confidentiality.
4. **Remote Signing and Telemedicine**:
- Enable secure remote access to records through NIP-46 for telehealth scenarios.
5. **Customizable Policies**:
- Tailor permissions and content filters to suit healthcare needs, such as restricting access to certain records or anonymizing sensitive data.
6. **Patient Empowerment**:
- Allow patients to manage access to their health information, promoting transparency and autonomy.
## Real-World Applications
Here’s how these tools can address specific healthcare challenges:
- **Secure Access to EHR:** Doctors and nurses can access patient records securely and efficiently, improving care coordination.
- **AI-Driven Diagnostics:** AI agents with predefined, limited permissions can analyze data for diagnostics while safeguarding privacy.
- **Telemedicine:** Secure, encrypted access ensures doctors can deliver remote care without compromising patient data.
- **Anonymized Research:** Controlled access to anonymized data can accelerate medical research while protecting privacy.
## The Bigger Picture
Decentralization is the key to fixing healthcare. Just like Bitcoin fixes the money and fixes the world - nostr and censorship-resistant encrypted data flow can fix whole industries like healthcare. By moving away from centralized, vulnerable systems, we can:
1. **Enhance Security:** Protect sensitive data from cyber threats with encryption and decentralized architectures.
2. **Lower Costs:** Reduce administrative overheads and eliminate inefficiencies.
3. **Improve Collaboration:** Foster better communication and coordination among healthcare professionals.
4. **Ensure Transparency:** Leverage open-source solutions to build trust and flexibility.
## Conclusion
The healthcare systems we have today are heavily reliant on money printing. They are have turned into businesses with overgrown administrative layer. They are inefficient and unsustainable. However, by adopting the Nostr protocol and tools built upon it, we can create a system that is secure, efficient, and patient-centric. With open-source tools like these, healthcare can truly focused on improving lives, become cheaper, more accessible, and abundant.
### Challenge
If you'd like to contribute to reinventing healthcare using free and open-source software built on the nostr protocol join the challenge by npub1healthsx3swcgtknff7zwpg8aj2q7h49zecul5rz490f6z2zp59qnfvp8p
note1lnh3q6648ysulrx2pgeyhv2cqqle9vftdxalq3yqkqa7c89eljtqyr70nl
-

@ f3df9bc0:a95119eb
2025-01-10 02:58:08
# MPT Equations
### Geometric Mean
$$
\bar{x} = (\prod_{i=1}^{n} x_i)^{1 \over n }
$$
### Covariance
$$
COV(x,y) = {1\over{n-1}} \sum_{i=1}^{n}{(x_i - \bar{x})(y_i - \bar{y})}
$$
where $\bar{x}$ and $\bar{y}$ are the **geometric** mean.
### Variance
$$
VAR(x) = {1\over{n-1}} \sum_{i=1}^{n}{(x_i - \bar{x})^2}
$$
### Standard Deviation
$$
\sigma_x=\sqrt{VAR(x)}
$$
### Correlation Coefficient
$$
\rho_{xy} = {COV(x, y) \over \sigma_x\sigma_y}
$$
### Portfolio Variance
$$
VAR(P) = \sum_{ij}w_i w_j COV(i, j)
$$
Where $w_i$ and $w_j$ are the normalized weight of the asset in the portfolio.
Note that this summation should include when $i = j$. In this case $COV(i, j) = VAR(i) = VAR(j)$
### Expected Return
$$
E_P = \sum_{i}w_i E_i
$$
Where $w_i$ is the normalized weight of the asset, and $E_i$ is the expected return of the individual asset.
-

@ 8d34bd24:414be32b
2025-02-12 17:38:19
All of us who have truly put our faith in the Lord Jesus Christ want to serve Him, but we all live busy lives. We all get distracted by making a living, taking care of our families, and other good things, but too often we spend so much time on the good that we miss out on the best (see “[Don’t Be Like Martha](https://trustjesus.substack.com/p/dont-be-like-martha)”). In this previous post, I wrote about how we don’t want to live. In this post, I’ll write about what the Bible says about living a life wholly devoted to God.
Many of us wonder, “Are we fully serving God if we aren’t in full time ministry, if we aren’t a pastor/priest, missionary, or if we don’t work for a Christian ministry?” There are many ways we can serve God. Sometimes we are called to a Christian “job,” but other times we serve God in other ways.
> Let the word of Christ richly dwell within you, with all wisdom teaching and admonishing one another with psalms and hymns and spiritual songs, singing with thankfulness in your hearts to God. **Whatever you do in word or deed, do all in the name of the Lord Jesus, giving thanks through Him to God the Father**. (Colossians 3:16-17) {emphasis mine}
The most important thing is that everything we do has a godly focus. We should follow God’s design for marriage and family. We should disciple our children to know and grow in Jesus. We should witness to those with whom we come in contact. We should give to support those who are working in full-time ministry. Even our jobs can be done in service to the Lord, no matter how trivial or unrelated that job might seem.
> **Whatever you do, do your work heartily, as for the Lord rather than for men**, knowing that from the Lord you will receive the reward of the inheritance. It is the Lord Christ whom you serve. (Colossians 3:23-24) {emphasis mine}
I’m an employer. I see the work ethic, or more often the lack of work ethic, in people. I notice those who work hard and always give their best versus those who do the minimum they need to do to keep their job. When a person lets everyone around them know that they are a Christian and then they work harder than everyone else and they are willing to do the undesirable tasks that need to be done, this is noticed and is a good witness. Sadly, too often Christians are known for not working as hard and not going the extra mile. These Christians give Jesus and all Christians a bad name. Whatever job God has given you, do it to the best of your ability. Do the extra task; do the undesirable task; do the task that should’ve been done by someone else. Put in the extra effort even if nobody seems to notice. In most case, even if you aren’t praised, appreciated, or appropriately rewarded, people do notice and your witness is enhanced. In all cases, Jesus notices and you will be rewarded in heaven for representing Him faithfully.
> Whether, then, you eat or drink or whatever you do, **do all to the glory of God**. (1 Corinthians 10:31) {emphasis mine}
We are to do everything we do to the God’s glory. The way we work should glorify God. The way we eat and drink should glorify God. The way we do rest and entertainment should glorify God. The way we interact with others should glorify God. We were designed to glorify God.
Too often we get busy doing life and leave God out of it. It isn’t that we are doing some terrible sin, but it is always wrong to leave God out of our life. We can even do Christian ministry and get so busy doing “God’s work” that we leave God out of it. This can be disastrous and definitely will damage ministry effectiveness. In everything we do, we should listen to God’s leading, whether through Bible reading, prayer, or being still and listening.
> The plans of the heart belong to man,\
> But the answer of the tongue is from the Lord.\
> All the ways of a man are clean in his own sight,\
> But the Lord weighs the motives.\
****Commit your works to the Lord\
> And your plans will be established**. (Proverbs 16:1-3) {emphasis mine}
Part of doing everything in and to the Lord is changing our hearts and minds. Psalm 37 lists several actions we can take in serving the Lord and becoming more like Him.
> **Delight yourself in the Lord**;\
> And He will give you the desires of your heart.\
****Commit your way to the Lord**,\
****Trust also in Him**, and He will do it.\
> He will bring forth your righteousness as the light\
> And your judgment as the noonday.\
****Rest in the Lord and wait patiently for Him**;\
****Do not fret** because of him who prospers in his way,\
> Because of the man who carries out wicked schemes.\
****Cease from anger and forsake wrath**;\
> Do not fret; it leads only to evildoing. (Psalm 37:4-8) {emphasis mine}
If we delight in the Lord, commit our way to the Lord, trust in Him, rest in the Lord, and wait patiently for the Lord, we will be in the right mind to serve Him in all that we do. It will also help us avoid the things that draw us away from the Lord. We are called to not fret, to cease from anger, and to forsake wrath. Fretting, anger, and wrath hurt our witness and draw us away from God. They are a sign that our hearts are not in tune with God and that we need to turn back to Him. They are a sign that we are not trusting in Him nor are we following His will.
---
Sometimes believers wonder if they are succeeding in doing anything for the Lord because they are shy and not good at witnessing or because they have personal circumstances (like sickness of themselves or their family members) that don’t allow them to do much. That doesn’t mean there is nothing these believers can do. We can support those doing the mission of God. We can give money to support missionaries, churches, and Christian ministries. We can house a missionary while they are on break. We can do behind the scenes tasks like cleaning, accounting, organizing, planning, etc.
Most importantly, we can all pray. Prayer should be a constant part of every day, whether we are infirm and unable to leave our bed, whether we are so busy we don’t have five minutes to sit and take a break, or whether we are in full time Christian ministry. We can’t faithfully serve God without prayer.
> Beloved, **you are acting faithfully in whatever you accomplish for the brethren**, and especially *when they are* strangers; and they have testified to your love before the church. You will do well to send them on their way in a manner worthy of God. For they went out for the sake of the Name, accepting nothing from the Gentiles. Therefore **we ought to support such men, so that we may be fellow workers with the truth**. (3 John 1:5-8) {emphasis mine}
Anyone who supports those in ministry will receive similar rewards to those in ministry because they are all working together to fulfill God’s will.
> He who receives a prophet in the name of a prophet shall receive a prophet’s reward; and he who receives a righteous man in the name of a righteous man shall receive a righteous man’s reward. (Matthew 10:41)
We often feel like we are failing God. We feel that we are making zero difference for the kingdom. If you are not growing in your faith, knowledge, and relationship with God, there may be some truth in this, but we also may be listening to the accuser, Satan. Keep in mind that every little thing you do for Jesus or for others, because of your faith in Jesus, is counted as faithful service to Him.
> “Then the King will say to those on His right, ‘Come, you who are blessed of My Father, inherit the kingdom prepared for you from the foundation of the world. For I was hungry, and you gave Me something to eat; I was thirsty, and you gave Me something to drink; I was a stranger, and you invited Me in; naked, and you clothed Me; I was sick, and you visited Me; I was in prison, and you came to Me.’ Then the righteous will answer Him, ‘Lord, when did we see You hungry, and feed You, or thirsty, and give You something to drink? And when did we see You a stranger, and invite You in, or naked, and clothe You? When did we see You sick, or in prison, and come to You?’ The King will answer and say to them, ‘**Truly I say to you, to the extent that you did it to one of these brothers of Mine, even the least of them, you did it to Me**.’ (Matthew 25:34-40) {emphasis mine}
Turn to Jesus. Pray to Jesus. Read His word —the Bible. Make Him a part of everything you do. Follow His leading. Join God in what He is doing.
May God bless you and lead you in the path He designed you to take.
Trust Jesus.
-

@ dd664d5e:5633d319
2025-01-09 21:39:15
# Instructions
1. Place 2 medium-sized, boiled potatoes and a handful of sliced leeks in a pot.

2. Fill the pot with water or vegetable broth, to cover the potatoes twice over.
3. Add a splash of white wine, if you like, and some bouillon powder, if you went with water instead of broth.

4. Bring the soup to a boil and then simmer for 15 minutes.
5. Puree the soup, in the pot, with a hand mixer. It shouldn't be completely smooth, when you're done, but rather have small bits and pieces of the veggies floating around.

6. Bring the soup to a boil, again, and stir in one container (200-250 mL) of heavy cream.
7. Thicken the soup, as needed, and then simmer for 5 more minutes.
8. Garnish with croutons and veggies (here I used sliced green onions and radishes) and serve.

Guten Appetit!
-

@ 88cc134b:5ae99079
2025-02-12 17:23:02
aaaaaa
-

@ d61f3bc5:0da6ef4a
2025-02-12 16:57:44
Micropayments on the Internet have been theorized for decades. However, it wasn’t until the emergence of Nostr that we’ve finally seen them deployed at scale. Nostr is still in its infancy, yet we are already witnessing an explosion of apps built on top of this open protocol. And most of them are featuring zaps! With the recent Primal 2.1 release, Nostr developers now have the option to enhance the experience for their users by integrating a Nostr-powered bitcoin wallet.
There is no doubt that micropayments add a new dimension to consumer apps. The incumbents have realized this and are rushing to add payments to their closed platforms. It won't be long before apps that don’t include built-in payments feel dated or outright broken. The question is not if apps of the future will have built-in payments, but what *kind* of payments they will be. Given that open networks have a tendency to win, our bet is that apps of the future will be powered by Bitcoin. Let’s see how Primal can help.
## Primal Wallet
Our vision for Primal Wallet is simple: deliver the smoothest transactional bitcoin wallet, endowed with expert Nostr skills. The wallet leverages Nostr’s open social graph as a de facto public lightning directory, while offering the highest level of user experience for Nostr’s rich content. For example, the user can scroll through the transaction list, select a zap, and drill straight into the conversation thread where the zap originated. The whole flow feels perfectly natural.

Since we launched Primal Wallet in December 2023, the user response has been incredibly positive. People love the idea of being able to post something on Nostr, get zaps from plebs around the world, then buy a coffee or a meal with those sats - all from the same app.
Having a bitcoin wallet with social skills resonated strongly with users, so Primal Wallet grew rapidly in popularity and usage. Since the launch, we have processed **1,338,460** transactions, with **238,916** just in the past month alone. This rivals some of the leading bitcoin wallets, and we are just getting started! We hear from many bitcoin OGs that they are using Primal Wallet as their transactional daily driver. Bullish.
All this is great, but something has been missing. Our users demanded the ability to connect Primal Wallet to other Nostr apps, so they can zap from anywhere in Nostr’s growing ecosystem.
## Zapping from Any Nostr App
For an existing Primal user, connecting the wallet to a new Nostr app can now be done in two clicks. Let’s take a look at how this is done from Olas, one of the most exciting new apps on Nostr:

Yes. Click, click. And you can start zapping!
Such smooth integration of payments is not available in any competing technology stack. Tradfi, fintech, crypto, etc., have nothing on Bitcoin and Nostr. Two clicks and your external wallet is connected. I’ll give you a moment now to allow for this new reality to settle in.
Primal enables you to connect any number of external apps and manage them from wallet settings:

Note that you can set your daily spend budget for each app or revoke its access at any time.
## How This Works
So, what is this sorcery? How does it work under the hood?
Connecting Nostr apps to external wallets is accomplished via the Nostr Wallet Connect protocol. It utilizes Nostr’s public relay infrastructure to enable communication between apps and wallets. You can learn more about this protocol [here](https://nwc.dev/), and access developer docs [here](https://docs.nwc.dev/).
The smooth, two-click connection setup UX is implemented through deep links between Primal and the external app. Here’s the deep link that the external app needs to call to invoke this feature:
```nostrnwc+primal://connect?appicon=[icon_url]&appname=[app_name]&callback=[callback_string]```
After the user clicks “Create Wallet Connection” in Primal, the Primal app calls the deep link defined in the callback, and passes the NWC connection string. That's all that the external app needs to make the wallet connection.
## What Comes Next?
The Nostr Wallet Connect protocol has been around for almost two years. Several bitcoin wallets implement it and many Nostr apps use it as their main way of enabling payments. What’s new with Primal 2.1 is the elevated user experience. Since Primal is a Nostr-powered wallet, it is aware of all the relevant metadata for each transaction: Nostr zaps, users, and the related events. Primal indexes the entire Nostr network, and now this is open to all Nostr apps that wish to integrate payments.
Nostr keeps expanding and getting better. Its openness enables us to build capabilities that lift all boats. The future is bright; I can’t wait to see how things evolve from here. 🍿🍿🍿
-

@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
## **Necessário**
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
## **Algumas coisas que você precisa saber**
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
---
## **O tutorial será dividido em dois módulos:**
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
---
## **No final, teremos:**
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

---
## **Módulo 1 - Criando uma carteira fria/assinador**
1. Baixe o APK do Electrum na aba de **downloads** em <https://electrum.org/>. Fique à vontade para [verificar as assinaturas](https://electrum.readthedocs.io/en/latest/gpg-check.html) do software, garantindo sua autenticidade.
2. Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

3. Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

4. Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o **modo avião**.\
*(Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)*

5. Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

6. No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. *(Aqui entra seu método pessoal de backup.)*

---
## **Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.**
1. Criar uma carteira **somente leitura** em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em <https://electrum.org/> ou da própria Play Store. *(ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)*
2. Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção **Usar uma chave mestra**.

3. Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em **Carteira > Detalhes da carteira > Compartilhar chave mestra pública**.

4. Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
5. Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: **Carteira > Addresses/Coins**.
6. Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

7. No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

8. No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
---
## **Conclusão**
**Pontos positivos do setup:**
- **Simplicidade:** Basta um dispositivo Android antigo.
- **Flexibilidade:** Funciona como uma ótima carteira fria, ideal para holders.
**Pontos negativos do setup:**
- **Padronização:** Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- **Interface:** A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: ***Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.***
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
---
-

@ 85bdb587:7339d672
2025-02-12 15:24:11
## Chart of the Day
While this is a bitcoin focused rag, I think it is important for any of you who read this to begin paying attention to gold markets if you haven't already. There has been an ongoing exodus of physical gold from London vaults and a rapid acceleration of gold being moved to the three biggest vaults in the United States in recent weeks. More gold has flooded into the US vaults over the first two months of this year than at the peak of the flight to safety during the beginning of the COVID lock downs.
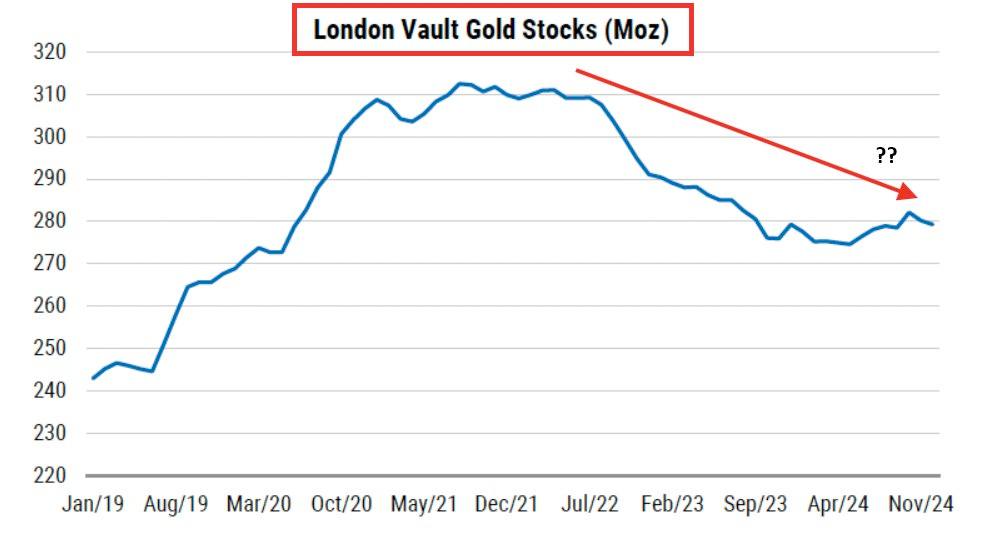
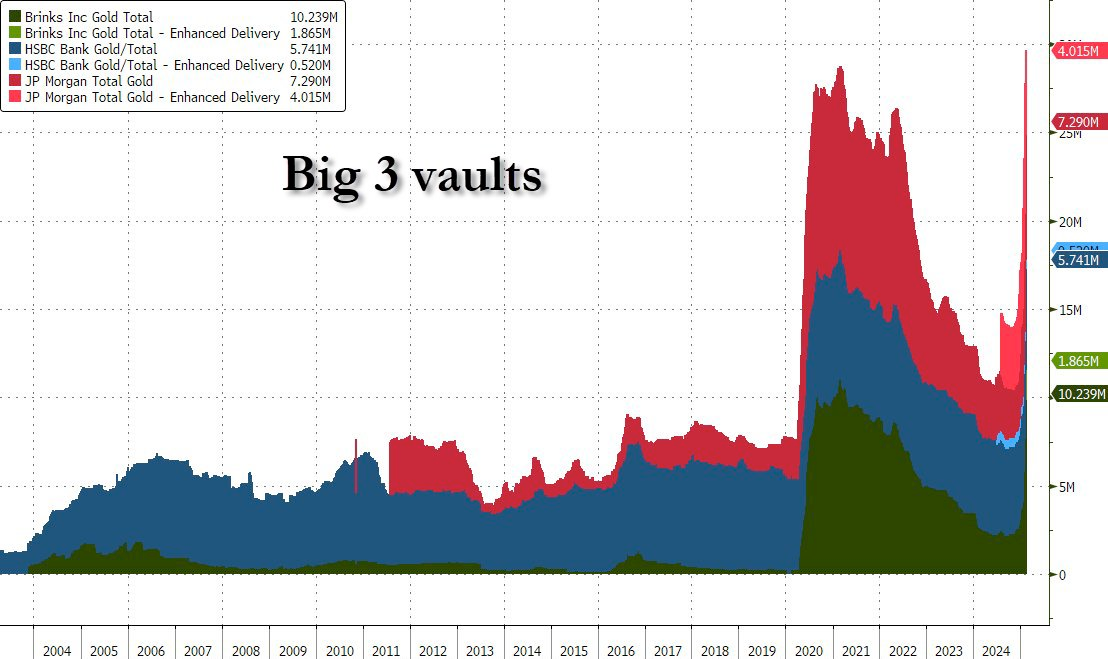
This is particularly perplexing considering the fact that equities are flat or up on the year, depending on the index you like to follow. Gold outperformed the S&P 500 significantly in 2024 and its momentum hasn't slowed down a bit in 2025 as the precious metal consistently hits new all time highs. The current correlation to the S&P 500 has only happened two times in history; right now and October of 2007.
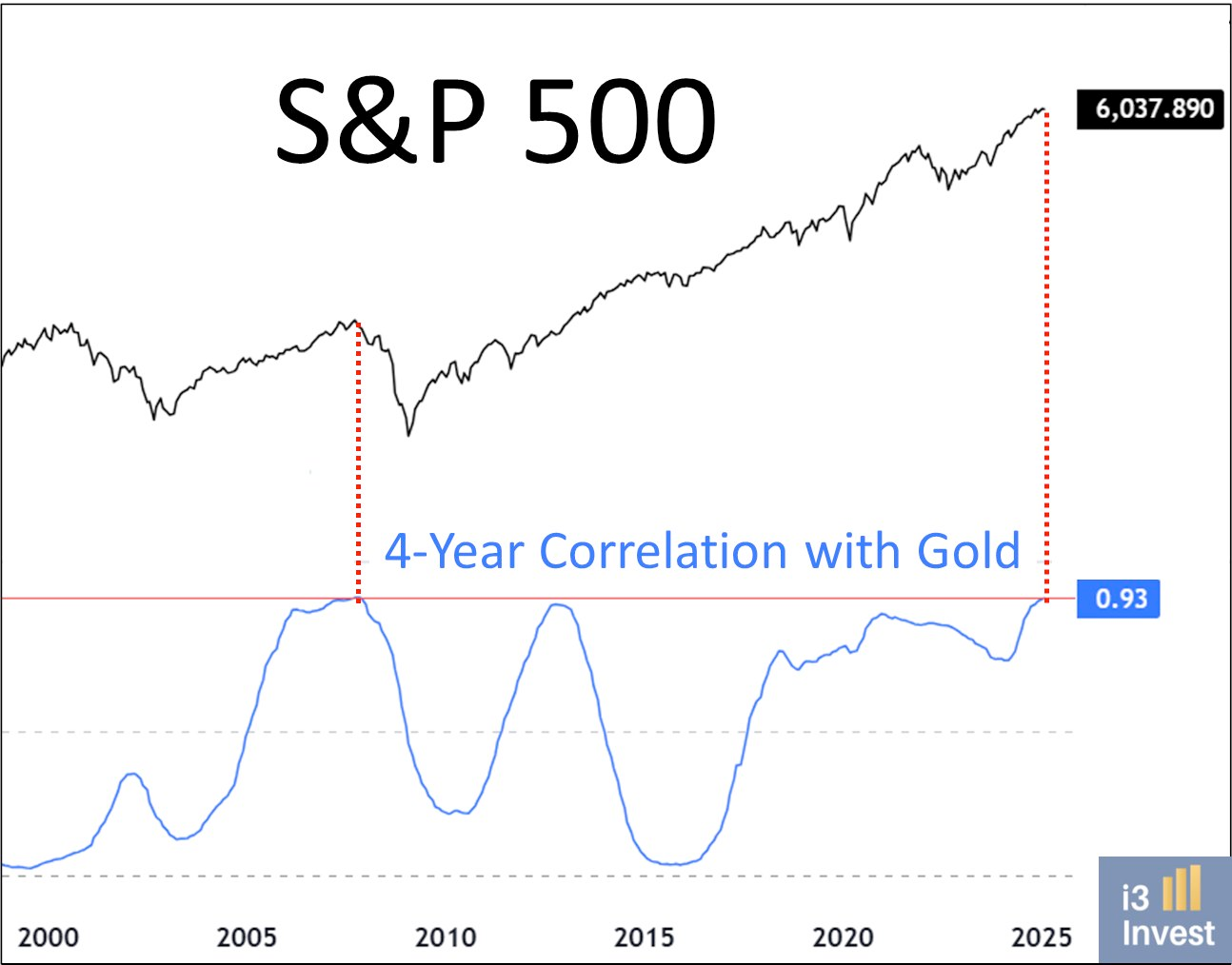
Institutional investors and nation states are piling into gold at an unprecedented pace. This signals that they are preparing for something to break. The catalysts for the exodus of gold from London to the US and from paper gold to physical gold are fears over Trump's tariffs, institutions and governments preparing for a potential monetary reset, and fears of a looming liquidity crisis as liquidity in the reverse repo market dries up. Uncertainty and chaos rule the day and we are witnessing a flight to safety.
Many of you are probably asking, "Why isn't bitcoin moving?!" That's a good question. Considering everything mentioned above one would think that bitcoin would be on the move toward new all time highs as well. Having been following bitcoin for twelve years your Uncle Marty has developed some pattern recognition when it comes to this market. Upward bitcoin price movements typically happen in a staircase fashion. Meaning that it trends up and to the right over the long-run with quick bursts to higher levels followed by small corrections and consolidation periods. If I had to guess, we are currently in a consolidation period that should come to an end at some point in the next few months. In recent years, gold has moved higher first and bitcoin has followed. Typically outperforming gold significantly. I find it hard to believe that this relationship is going to end any time soon. Especially considering the geopolitical and economic backdrop.
## Luke Gromen Warns Bitcoin Holders: Historical Currency Revaluations Show Speed Matters
During my recent conversation with Luke Gromen, he raised a sobering point about the velocity of monetary regime changes. Drawing from historical examples, including a Ukrainian family who saw their savings devalue from "five cars to one month's groceries" over a single weekend, Luke emphasized that Americans are uniquely blind to how quickly these transitions can occur. The current stress in our financial system - from Treasury market dynamics to global trade tensions - suggests we're approaching a similar inflection point.
*"What if they do it on Friday night like they did with Trump coin and you wake up and gold's up 1,000% by the time you're up on Saturday morning, what are you going to do? You're going to sell your bonds and buy gold on Saturday?"* - Luke Gromen
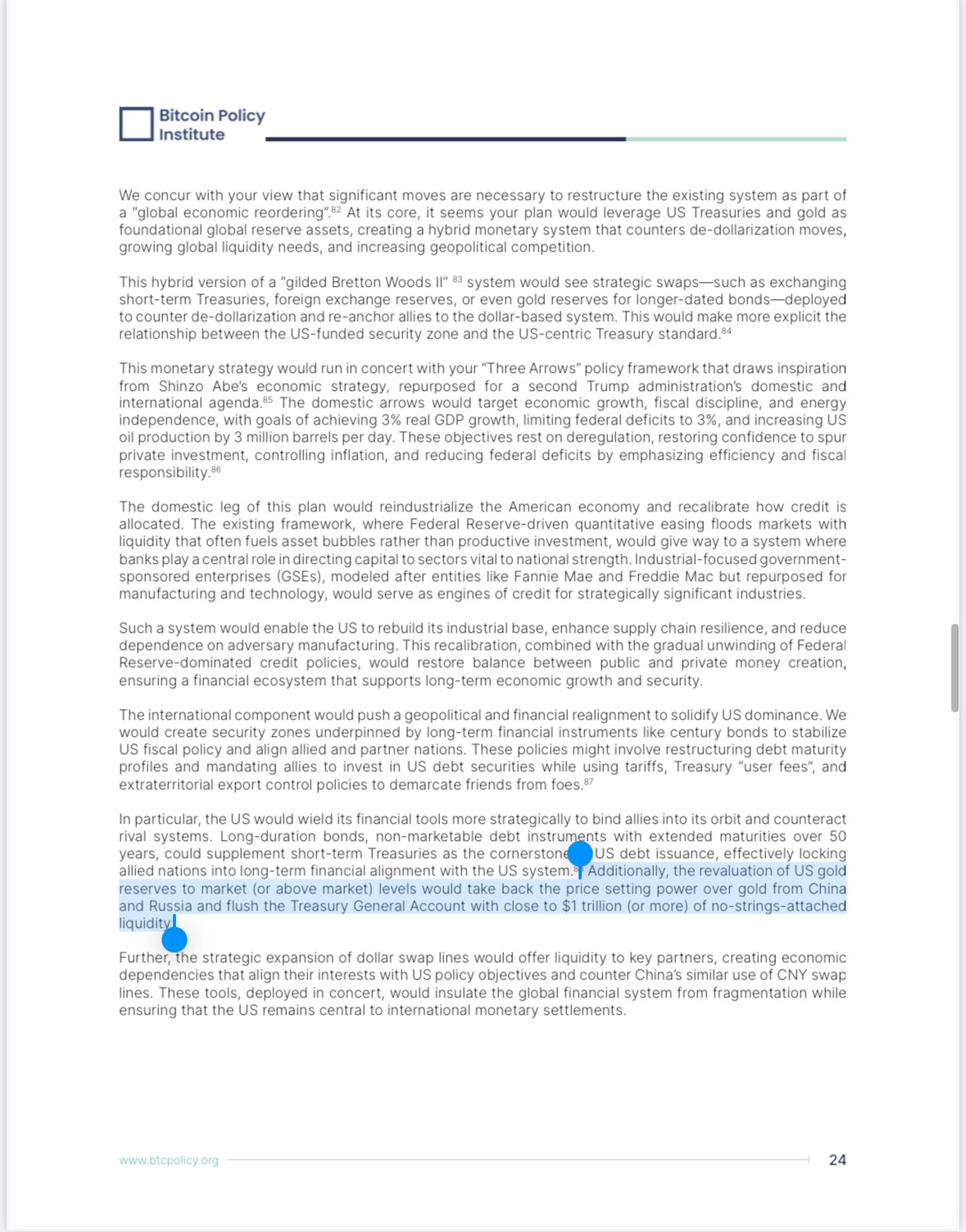
This warning shouldn't be taken lightly. Those waiting for clear signals before acquiring bitcoin may find themselves locked out of the transition entirely. Luke's analysis suggests that rather than a gradual shift, we're more likely to see a compressed timeframe where major monetary changes happen over days or weeks, not months or years. The recent Trump coin phenomenon, while different in nature, demonstrates how quickly markets can move when sentiment shifts dramatically.
TLDR: Major monetary changes happen fast - don't wait to stack sats.
Check out the full podcast [here](https://www.youtube.com/watch?v=RCeWQHATWYU&t=61s&ab_channel=TFTC&ref=tftc.io) for more on DeepSeek's impact on AI markets, Colombia's trade negotiations, and Scott Percent's three arrows for economic reform.
## Headlines of the Day
U.S. Faces $1.67B Annual Cost Spike on Single Bond Rollover - via [X](https://x.com/TFTC21/status/1889454272842268982)
BlackRock: Bitcoin is Monetary Hedge, Ethereum is Tech Play - via [X](https://x.com/BitcoinNewsCom/status/1889396849880268814)
Lummis: SBR Could Slash U.S. Debt by 50% in Two Decades - via [X](https://x.com/cryptonwsuk/status/1888565117047951869)
Fold Launches Bitcoin Rewards Visa Credit Card - via [Business Wire](https://www.businesswire.com/news/home/20250211765772/en/Fold-Launches-Revolutionary-Bitcoin-Rewards-Visa-Credit-Card)
Obscura VPN launches with a MacOS product - via [nobsbitcoin.com](https://www.nobsbitcoin.com/obscura-vpn-is-now-available-on-macos/)
## Bitcoin Lesson of the Day
The SegWit (Segregated Witness) upgrade in August 2017 made two key changes to Bitcoin. First, it moved transaction signatures to a separate part of the data, fixing "transaction malleability" by preventing nodes from modifying transaction IDs. Second, it increased effective block capacity by introducing "weight units" that gave signature data a 75% discount, allowing blocks to grow from 1MB to about 1.8MB.
As a "soft fork," SegWit remained compatible with older Bitcoin software. The upgrade activated at block 481,824 after 95% of miners signaled support. This approach allowed Bitcoin to increase capacity and fix technical issues while maintaining network compatibility.
[SegWit - Learnmeabitcoin.com](https://learnmeabitcoin.com/beginners/guide/segwit/?ref=tftc.io)
ICYMI Fold opened the waiting list for the new Bitcoin Rewards Credit Card. Fold cardholders will get unlimited 2% cash back in sats.
[Get on the waiting list now](https://foldapp.com/credit-card?r=BgwRS) before it fills up!
$200k worth of prizes are up for grabs
.
The Fold Bitcoin Rewards Credit Card waitlist is live!
*Ten31, the largest bitcoin-focused investor, has deployed $150M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/funds.*
Subscribe to our YouTube channels and follow us on Nostr and X:
[TFTC YouTube](https://www.youtube.com/tftc21)
[Bitcoin Brief YouTube](https://www.youtube.com/@BTCBrief)
[TFTC on Nostr](https://primal.net/tftc)
[TFTC on X](https://x.com/tftc21)
-

@ 94a6a78a:0ddf320e
2025-02-12 15:05:48
Azzamo is more than just a relay provider—it’s a **high-performance network** designed to make Nostr **faster, smoother, and more reliable** for everyone. Whether you're **posting notes, zapping sats, sharing media, or sending DMs**, Azzamo keeps your Nostr experience **seamless and efficient**.
Nostr is unstoppable, but **not all relays are the same**. Some are **slow, unreliable, or disappear overnight**, while others get **overloaded**, making message delivery **inconsistent**. Azzamo is built differently—offering **fast, stable, and globally distributed relays** to ensure **low-latency, high-speed connections**, no matter where you are.
---
## **🌍 Premium Relays for Maximum Performance**
Azzamo **Premium Relays** are optimized for **speed, reliability, and uptime**, available exclusively to **Premium users**:
📡 **Azzamo Premium Relays:**
- **Europe:** `wss://relay.azzamo.net`
- **America:** `wss://us.azzamo.net`
- **Asia:** `wss://asia.azzamo.net`
Add **Azzamo Premium Time** to **unlock unlimited, high-speed access** across these global relays.
🔗 **Get Premium:** [azzamo.net/premium](https://azzamo.net/premium)
---
## **🆓 Freemium Relays – Free for Everyone**
Azzamo believes in **keeping Nostr open** and accessible to all. That’s why we offer **free relays for everyone**, with **no rate limits for Premium members**
📡 **Freemium Relays:**
- **Free Relay:** `wss://nostr.azzamo.net` – Open to all.
- **Inbox Relay:** `wss://inbox.azzamo.net` – Reliable for DMs & group messages.
By offering both **free and premium options**, Azzamo ensures that **anyone can use Nostr, while also funding the infrastructure that keeps it running smoothly.**
---
## **🛡️ Minimal Moderation, Maximum Transparency**
Nostr is about **free speech**, but that doesn’t mean **zero moderation.** Azzamo follows a **minimal moderation policy** to keep relays **functional and spam-free** while maintaining **transparency** in enforcement.\
\
🚫 **Spam & network abuse**\
🚫 **Illegal content (CSAM, fraud, malware, scams)**\
🚫 **Impersonation & identity abuse**
We also maintain a **public Ban API** for **transparent moderation decisions**.
📖 **More on our Ban API:** [azzamo.net/introducing-the-azzamo-ban-api](https://azzamo.net/introducing-the-azzamo-ban-api)
---
## **🚀 Get Started with Azzamo Relays Today!**
🔗 **Connect now:**\
📡 `wss://nostr.azzamo.net` (Freemium Free Relay)\
📬 `wss://inbox.azzamo.net` (Freemium Inbox Relay)\
📡 `wss://relay.azzamo.net` (Premium Europe Relay)\
📡 `wss://us.azzamo.net` (Premium Americas Relay)\
📡 `wss://asia.azzamo.net` (Premium Asia Relay)
Nostr is growing fast. **Make sure your relays can keep up.** 🚀
#azzamo #grownostr #nostr #relay #relays #premiumrelay #paidrelay
-

@ dd664d5e:5633d319
2025-01-07 19:57:14
## Hodling Bitcoin does not make you a capitalist
I've noticed that Bitcoin-mindedness seems to lead some people to communistic thinking because it's a hard-limited form of capital. Marx, like most Bitcoiners, heavily discounted the possibility of economic growth or transformation changing the economy enough to undermine some minority's control of some form of capital.
What few today understand, is that many of the Dirty Capitalists of Marx's era actually agreed with him; they were just disdainful of labor and worried that the workers finding out that Marxism is correct about the nature of capitalism would cause unrest. They were the original HFSP crowd.
This was the basic idea, that Marx had, and that many Bitcoiners would agree with:
> Capital is strictly limited and the people that control it can keep labor from attaining any, except when their labor is necessary.
And, as we know, automation will make human labor increasingly unnecessary.
## The math doesn't check out
That underlies all of the calculations of "Well, if I just grab this Bitcoin wallet and hodl for twenty years, then it will grow in value to equal half of everything in existence and then I can just buy up half the planet and rule over everyone like a god."
This is economic nonsense because it assumes that:
1) the value of all things remains static over time,
2) purchasing something with money gives you ownership of it,
3) people will always use that specific money (or any money, at all!) for all transactions,
4) there is no such thing as opportunity cost,
5) people will always value money more than any other thing, and therefore be willing to always trade it for anything else,
6) humans are passive, defenseless, and easy to rule over,
7) someone who is preoccupied with hodling an asset steadily and sharply rising in price would ever be emotionally ready to part with it.
## All monies can die.
People use money for everything because it is easy, fast and cheap. If money becomes too precious or scarce, they will simply switch to using other things (as we saw with gold). Humans replace tools that aren't working well, with those that work better, and money is just another tool. Bitcoin is more divisible than gold, but that won't matter, if enough of it is held by too few.
This is why there's a natural cap on the price of a money and why human productivity _in the here and now_ is not irrelevant or in vain.
-

@ 5d4b6c8d:8a1c1ee3
2025-02-12 14:36:40
Here are today's picks using my proprietary betting strategy at [Freebitcoin](https://freebitco.in/?r=51325722). For details about what Risk Balanced Odds Arbitrage is and why it works see https://stacker.news/items/342765/r/Undisciplined.
For a hypothetical 1k-ish wager on each match, distribute your sats as follows:
| Outcome 1 | Outcome 2 | Outcome 3 | Bet 1 | Bet 2 | Bet 3 |
|--------------|-------------|--------------|-------|-------|-------|
| Juventus| Inter Milan| Draw | 294| 435| 303|
| Tottenham| Man United| Draw | 406| 357| 266|
| Liverpool| Wolves| Draw | 833| 67| 125|
| Valladolid| Sevilla| Draw | 222| 500| 289|
| Real Betis| Real Sociedad| Draw | 393| 321| 313|
| Osasuna| Real Madrid| Draw | 174| 619| 227|
| Barcelona| Rayo Vallecano| Draw | 818| 80| 133|
| Atletico Madrid| Celta Vigo| Draw | 692| 118| 217|
I'll be curious to see how @Coinsreporter does with his modified RBOA.
On the most recently completed sets of RBOA, I lost 700 sats on about 50k wagered. I'm not sure if that's just normal variance or if it's due to matches not being posted as far in advance, which reduces the early mover bonus.
I still haven't precisely identified where the threshold is, but it might be worth skipping any of these with a "time weight multiplier" lower than 90.
----------
A note of caution about Freebitcoin: they recorded the wrong outcome for last week's Bills vs Ravens game and as of yet have not corrected it. I recall one other instance of something similar happening, so proceed with caution.
This RBOA strategy is largely immune from that problem, but be aware of it when just betting on one outcome.
originally posted at https://stacker.news/items/883708
-

@ 207ad2a0:e7cca7b0
2025-01-07 03:46:04
*Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my [free to read/share attempt to write a novel](https://untitlednovel.dns7.top/contents/), but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.*
Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end.
Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:
and after a number of outputs, selected this one to work on:
The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.

The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.
At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.
At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:

Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story.
#### The AI Generated Elephant in the Room
If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it.
I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points.
I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs.
-

@ dd664d5e:5633d319
2025-01-06 20:36:17
_Ingredients_
* 1 kg of pork roast with rind, such as shoulder or a lean belly
* 1 bottle of beer, light or dark
* chopped German-style mirepoix (best combination, for this recipe, includes celery root, carrot, red onion, and leeks)
* salt, pepper, nutmeg
* 1 diced garlic clove
_Directions_
1. Spread the vegetables on the bottom of the roasting pan.
2. Pour half the beer over the roast. (Drink the other half.)
3. Season the meat, to taste.
4. Roast the meat at 180 °C, until done (depends upon the weight of the roast).
5. Remove the meat from the oven, and wrap in aluminum foil.
6. Pour 2-3 cups of water into the roasting pan.
7. Pour/scrape everything from the pan into a sieve over a sauce pot.
8. Press the vegetables against the sieve, with the back of a spoon, to ensure that you get all that good dripping flavor into the sauce.
9. Defat the sauce with a grease separator, then pour it back into the pot.
10. Thicken the sauce, slightly (it should remain slightly watery, and not turn into a gravy), according to your usual method.
11. Open the foil and slice the roast.
12. Serve with the sauce.








-

@ e6817453:b0ac3c39
2025-01-05 14:29:17
## The Rise of Graph RAGs and the Quest for Data Quality
As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence.
## Booming Interest in Graph RAGs
Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can:
* **Enhance LLM Outputs:** By grounding responses in structured knowledge, graphs significantly reduce hallucinations.
* **Support Complex Queries:** Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving.
Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs?
## Data Quality: The Foundation of Effective Graphs
A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why:
* **Richness of Entities:** Effective retrieval depends on graphs populated with rich, detailed entities.
* **Freedom from Hallucinations:** Poorly constructed graphs amplify inaccuracies rather than mitigating them.
Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs.
## Hybrid Graph RAGs and Variations
While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that:
* Handle diverse data sources with ease.
* Offer improved adaptability to complex queries.
Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing.
## Ontology: The Key to Graph Construction Quality
Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for:
* **Defining Relationships:** Clarifying how concepts connect within a domain.
* **Validating Graph Structures:** Ensuring constructed graphs are logically sound and align with domain-specific realities.
Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs?
## How to Build Ontology Expertise in a Startup Team
For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach:
1. **Assign a Knowledge Champion:** Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering.
2. **Provide Training:** Invest in courses, workshops, or certifications in knowledge graph and ontology creation.
3. **Leverage Partnerships:** Collaborate with academic institutions, domain experts, or consultants to build initial frameworks.
4. **Utilize Tools:** Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process.
5. **Iterate with Feedback:** Continuously refine ontologies through collaboration with domain experts and iterative testing.
So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts.
You could read about barefoot experts in my article :
Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise.
## How to Find or Create Ontologies
For teams venturing into Graph RAGs, several strategies can help address the ontology gap:
1. **Leverage Existing Ontologies:** Many industries and domains already have open ontologies. For instance:
* **Public Knowledge Graphs:** Resources like Wikipedia’s graph offer a wealth of structured knowledge.
* **Industry Standards:** Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields.
* **Business Framework Ontology (BFO):** A valuable resource for enterprises looking to define business processes and structures.
1. **Build In-House Expertise:** If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation.
2. **Utilize LLMs for Ontology Construction:** Interestingly, LLMs themselves can act as a starting point for ontology development:
* **Prompt-Based Extraction:** LLMs can generate draft ontologies by leveraging their extensive training on graph data.
* **Domain Expert Refinement:** Combine LLM-generated structures with insights from domain experts to create tailored ontologies.
## Parallel Ontology and Graph Extraction
An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as:
* **Detecting Hallucinations:** Differentiating between genuine insights and AI-generated inaccuracies.
* **Ensuring Completeness:** Ensuring no critical concepts are overlooked during extraction.
Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method.
## LLMs as Ontologists
While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to:
* **Generate Skeleton Ontologies:** Prompt LLMs with domain-specific information to draft initial ontology structures.
* **Validate and Refine Ontologies:** Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance.
However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes.
## Final Thoughts: Unlocking the Power of Graph RAGs
The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools.
As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding.
Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation!
-

@ c4b5369a:b812dbd6
2025-02-12 12:23:40

### Unidirectional payment channels revisited
#### Nodeless lightning - Reduce ecash mints custodial risk
---
### Sats N Facts
The nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx unconference has just wrapped up. And what a blast it was. In the heart of northern Thailand, developers, researchers, content creators and more, came together to share ideas on how Bitcoin, Nostr and other free protocols are being used everyday to liberate people.
Not only were stories shared from different community leaders on how embracing bitcoin has empowered them and their communities, but a big goal of the unconference was to bring bitcoin engineers and developers from various domains together in one room, unstructured, chaotic, and let them do their thing.
At first, I thought not having a schedule might be boring, but oh boy was I wrong. There was so much stuff going on, it was hard to choose which session I would have to miss!
### Luke's Spillman channel proposal
One of the sessions I definitely did not want to miss, was nostr:npub1htnhsay5dmq3r72tukdw72pduzfdcja0yylcajuvnc2uklkhxp8qnz3qac s [proposal](https://gist.github.com/lukechilds/307341239beac72c9d8cfe3198f9bfff)
> Ecash mints funded with Spillman channels: The ultimate nodeless Lightning wallet
.
In true unconference fashion, he announced in the main room that the session was about to start, and that the people that are interested should meet him in the whiteboard corner in 10 minutes. The corner was packed, and Luke explained his proposal.
### What's a "[Spillman channel](https://en.bitcoin.it/wiki/Payment_channels#Spillman-style_payment_channels)"?
Essentially when we are talking about Spillman channels, what is meant are unidirectional payment channels (or [CLTV-style channels](https://en.bitcoin.it/wiki/Payment_channels#CLTV-style_payment_channels)). An unidirectional payment channel means, only one party can send payments, but not receive, and the other party can only receive, but not send. They also expire after a predetermined amount of time, and must be closed.

At first glance, this might look kinda stupid. After all, we have [Poon-Dryja channels](https://en.bitcoin.it/wiki/Payment_channels#Poon-Dryja_payment_channels) that are powering the lightning network. They are bi-directional, do not expire, and can be used to shuffle coins back and forth theorethically an unlimited amount of times.
So, why bother with this stupid one-way channel?
### Simplicity is king
People that have worked with lightning channels can sing you a song about complexity, state handling and risks about the current state of bidirectional payment channels. Essentially, There are a lot of requirements on both channel parties when it comes to Liveness (being online) and also state handling (continuous backups).

In some cases, especially when in the context of end-users wanting to perform payments on their mobile phone, they would appreciate it if there was not so much complexity and overhead involved.
The gist of the idea is to combine unidirectional channels and ecash mints to achieve the following:
A self custodial unidirectional payment channel to an ecash mint, massively reducing the senders liveness and state handling requirements when compared to a lightning channel. Sending payments through the mint will be done through swapping some of the channel balance for ecash tokens. At this point, the user is trusting the mint to honor the redemption of these tokens, while the remaining channel balance remains in self custody. This gives them better controll over their funds than just holding their entire balance custodied in the mint. The ecash tokens can then be redeemed to pay a lightning invoice, just the same as it is done now with normal cashu mints.

So this channel, that has no liveness or state management requirements for the sender, and must have a pre-defined close time, seems to be a perfect fit for the following usecase:
1. A `sender` receives his salary once a month. He opens a channel that is valid for one month.
2. The `sender` then can do his daily spending over this channel. He only trusts the `mint` with the amount for the current outgoing payment while it is swapped for ecash, waiting for redemption.
3. If the `sender` must receive funds (a refund for example), he can do so into the `mints` custody, by receiving ecash. He can spend his ecash funds first when doing his next payment, to reduce his custodial exposure.
4. When the channel expires, or runs out of funds, the `mint` closes the channel.
From a consumer perspective, that just want to receive his salary and make frequent payments afterwards, this usecase seems to make a lot of sense. Obviously from a merchants perspective on the other hand, such a channel doesn't really work. But that's fine, it's not the problem we're trying to solve here.
What do you think of this idea? Be sure to let me know in the comments!
In the next article, we will dive into how such a system can be implemented today, using Bitcoin, Cashu and Lightning. We will also discover how the system can be improved, to make channels non-expiring (A collaborative idea between nostr:npub148jz5r9xujcjpqygk69yl4jqwjqmzgrqly26plktfjy8g4t7xaysj9xhgp and nostr:npub1htnhsay5dmq3r72tukdw72pduzfdcja0yylcajuvnc2uklkhxp8qnz3qac born at nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx ).
So stay tuned!
-

@ f3df9bc0:a95119eb
2025-01-03 21:36:45
# MySql InnoDB Indexes for Developers
This article aims to be a high level reference for developers who just want to use Mysql InnoDB indexes effectively. Although you _can_ read this from top to bottom, I'd encourage you to save time by skipping to sections that interest you using the below table of contents.
# Contents
- [Quick Reference](#quick-reference) (Start here for guidelines you can use right away, without needing the _why_)
- [Index Structure](#index-structure)
- [Primary Index Structure & Paging](#primary-index--paging)
- [Secondary Indexes](#secondary-index-structure)
- [Composite Indexes](#composite-index-structure)
- [Index Navigation](#index-navigation)
- [ref-type Queries](#ref-type-queries)
- [range-type Queries](#range-type-queries)
- [Post-Index Computations](#post-index-computations)
- [Join Algorithms](#join-algorithms)
- [Nested Loop Join](#nested-loop-join)
- [Hash Join](#hash-join)
- [Compound Cursor Iteration](#compound-cursor-iteration)
<style type="text/css">
.box {
background: #cedce8;
padding: 1px 10px 5px 10px;
border-radius: 15px;
}
.box code {
background: #bfd7ec;
}
</style>
<div class="box" style="" markdown="1">
# Quick Reference
This is a quick list of the practical guidelines that you can use to make your applications more performant at the database layer. We'll dive into the _why_ each of these things are true, and give you mental models such that you can arrive at these guidelines yourself _without memorization_, at later sections of the article.
<button onclick="toggle_quickref();">Click To Expand ▼</button>
<script type="text/javascript">
function toggle_quickref() {
var x = document.getElementById("quick-reference-body");
if (x.style.display === "none") {
x.style.display = "block";
} else {
x.style.display = "none";
}
}
</script>
<div id="quick-reference-body" style="display:none" markdown="1">
**Structure**
- Every non-`PRIMARY` index is really a compound index with the `PRIMARY` index.
- `[foo]` is implicitly `[foo, id]`, likewise `[a, b]` is implicitly `[a, b, id]`
- Usually prefer high cardinality columns (those with many unique values) to come earlier in indexes.
- For example IDs have more unique values than boolean flags, so put the ID first in the index `[account_id, is_active]`
- *Note:* there are exceptions, especially when range queries are involved
- Only `SELECT`-ing columns contained in the index will significantly reduce memory paging.
- eg `SELECT foo, id` when the index `[foo]` is being used.
**Filtering**
- An index must be "used" from left to right. Given an index of `[a, b, c]`:
- 🟢 `WHERE b=2 AND a=1` will correctly use the `[a, b]` portion of the index
- 🟡 `WHERE a=1 AND c=4` will only use the `[a]` portion of the index
- 🔴 `WHERE b=5` will not be able to use this index at all
- A range filter prevents any columns to the "right" from being used. Given an index of `[a, b, c]`:
- 🟡 `WHERE a=1 AND b>4 AND c=10` will only use the `[a, b]` portion of the index
- 🔴 Implied by this is that queries containing ranges on two or more columns **cannot** be solved by indexes `WHERE a>5 AND b>2`
- Any filters that aren't solved as part of the index will require linear row scanning. The performance of this is correlated to the "hit ratio".
- Given an index of `[a]`, the performance of `WHERE a=1 AND c=4` will correlate to *what percentage of `a=1` rows also have `c=4`*. If this percentage is low, performance will be worse. Put another way: if there are a large number of rows where `a=1` but only a couple of those also have `c=4`, mysql will need to search through and discard many rows.
**Ordering**
- Indexes naturally return rows ordered by their structure.
- Selecting from index `[a, b]` will naturally give rows ordered by `[a, b, id]`
- Any unnatural ordering will require a O(nlogn) **filesort**, which can be very slow for large amounts of rows
- With an index of `[a]`, the query `WHERE a=1 ORDER BY b` will need to sort all rows that meet the filtering clause.
- Columns on the "left" of the index can be efficiently excluded from the `ORDER BY` clause, **if** they have been used in the `WHERE` clause as a **non-range** filter.
- Given an index of `[a, b]`, with a natural ordering of `[a, b, id]`:
- 🟢 `WHERE a=1 ORDER BY b,id` is also natural ordering
- 🔴 `WHERE a=1 ORDER BY id` is **not** natural ordering
- 🟢 `WHERE a=1 AND b>10 ORDER BY b,id` is natural ordering
- 🔴 `WHERE a=1 AND b>10 ORDER BY id` is **not** natural ordering
- 🟢 `WHERE a=1 AND b=2 ORDER BY id` is natural ordering
- 🟢 `WHERE a=1 AND b=2 AND id>5 ORDER BY id` is natural ordering
**Limit & Offset**
- Performance of `LIMIT` is correlated to the "hit density" when scanning rows. eg are the rows you're scanning for abundant? Or will mysql need to scan for a long time to find enough rows?
- `LIMIT` is applied **after** sorting, so will not improve the performance of a filesort
- Performance of `OFFSET n` is correclated to the value of `n`. Therefore it is not a good fit for pagination as the query will get slower as `n` increases.
</div>
</div>
-----
# Index Structure
Indexes are constructed from a B+tree structure. Understanding this structure is key to gaining an intuitive reasoning for how queries will perform using different indexes. Both the `PRIMARY` index and secondary indexes have a similar tree structure, differing only in what data is stored on the leaves of the tree.
## Primary Index Structure & Paging
Looking at the structure of a `PRIMARY` index first, we see that the full row is stored in each leaf of the tree, and each leaf is ordered sequentially on the disk:

<center><small style="color: #999">note: page size greatly reduced for illustration</small></center>
If possible, it is best to select the primary index for a table with data locality in mind, to reduce how many page loads need to take place to satisfy a query. For example, imagine a blogging application that almost always queries for posts on a specific blog: `SELECT * FROM posts WHERE blog_id=10`. Ideally we'd like for this table to have all the posts where `blog_id = 10` stored **sequentially** in the primary index. However, by using a standard primary index on `[id]` we see a structure where rows are stored in disk pages in the order they were **created**. The diagram below illistrates this (ID integer, colour coded by blog)

By insteading using a **composite primary key**, this table can be made much more efficient given its access pattern. In the below diagram I show the same data, but instead stored in a composite primary index of `[blog_id, id]`. This means rows are first sorted by `blog_id`, and then by `id` for each blog. When the data is stored in this manner, our query for `SELECT * FROM posts WHERE blog_id=10` is likely to load less pages from disk.

## Secondary Index Structure
Secondary indexes have a similar structure to that of primary indexes. However, instead of storing the _full row_ in the leaves of the tree, only the primary index value is stored:

This structure means that if additional columns are required (eg a `SELECT *`), then after traversing the secondary index, mysql must also traverse the primary index _for each selected row_ to actually load the required data. By only selecting columns available in the secondary index, mysql can skip this extra lookup step.
## Composite Index Structure
When multiple columns are specified in a compound index, we get a structure composed of **nested B+trees**. This is where the ordering of columns within an index definition becomes relevant. The root of the tree is defined by the _first_ column in the index definition, the second nested tree would be the _second_ column in the index definition, and so on.
The below diagram is the structure of a composite index `[blog_id, created_at]` (with the implied `id` column on the end):

# Index Navigation
We'll now look at how mysql navigates these indexes given various query structures, which should help give an intuitive understanding for why Mysql performance will vary.
## `ref`-type queries
With this tree-based model in place, we can see that to efficiently use an index like this we must navigate the tree _in the order that the index is defined_. If our query does not specify a value for all columns in an index, this is ok as long as the values we _do_ provide are at the top of the tree.
I've illustrated below two examples of the "happy path" for navigating a `[blog_id, user_id]` index. In the first, we have provided a filter on both `blog_id` and `user_id`, which allows for mysql to fully navigate the tree to the leaves. In the second, we only provide a filter on `blog_id`, but because this is the first column in the index mysql is still able to efficiently select all the rows that meet this criteria (it selects **all leaves from the sub tree**)

<div class="box" style="" markdown="1">
💡 Notice how the ordering of the rows appears to change depending on **how far mysql navigates the tree**. Rows in an index are always stored in the same ordering scheme as the index itself. That is to say that a `[blog_id, user_id]` index will naturally store rows in `blog_id, user_id, id` ordering. However, as we navigate further into the tree the ordering appears to "simplify". If we are selecting rows for a specific `blog=10 and user_id=50` then the rows appear to be ordered by `id`, because they all share the same values for both blog_id and user_id!
</div>
## `range`-type queries
The range-type lookup happens when a query selects _multiple values_ for an indexed column. There are many ways a query could end up in this scenario:
- `WHERE updated_at > X`
- `WHERE user_id != X`
- `WHERE blog_id IN (1, 5, 34, 200)`
- `WHERE user_id=10 OR user_id=50`
In such cases, mysql will need to navigate _multiple branches_ of the index. Consider the below query where we search for all recently created posts for a particular blog:

There are two things I'd like to point out about this pattern:
1. The ordering of the results is `created_at, id`. Sorting by `id` (for example) is not possible without a `filesort` operation.
2. There is no efficient way to navigate the deeper sections of the tree (ie the `id` portion of the index above) without iterating through all the selected branches of `created_at`. That is, if we were to add an additional filter on `id > 5` for example, then there is no single tree to navigate and provide these values. Mysql would instead need to iterate through every sub-tree (one per value of `created_at`) to complete this filtering operation (see diagram below)
A common application pattern that can suffer performance issues due to both these points is *ID-based pagination* (ie if your pagination system needs to filter on `WHERE id > x ORDER BY id`). See the section on [compound cursor iteration](#compound-cursor-iteration) for a potential solution.

# Post-Index Computations
Although Mysql will always start off by using an index if possible to reduce the amount of post-processing required, it goes without saying that not every query will be fully solved by an avilable index. There are a couple post-index computations that we should consider the relative performance of.
First, if the query is requesting an `ORDER` which differs from how the index sorts its rows, a filesort will be required. This is an expensive operation (`O(nlogn)`) if the number of rows to be sorted is large. In addition, sorting requires Mysql to temporarily buffer the entire dataset (eg you can't stream a sorting operation). See [ref-type queries](#ref-type-queries) for a reminder how indexes naturally sort rows.
If the `WHERE` clause of the query was not fully solved by the index, Mysql will also need to scan through the rows one after another to apply the remaining filtering. While this is faster than a filesort, it is also relatively slow for large data sets (`O(n)`). If the index reducing the dataset down to a reasonable size upfront, then this may not be a big deal.

There is one exception here: if the query also specifies a `LIMIT x`, Mysql need not scan the _entire_ dataset. Mysql will "short circuit" the row scan as soon as it has enough rows to satisfy the query condition. The performance of this kind of pattern is dependent on the "hit ratio" of rows. If there are relatively few rows that satisfy the filter condition compared to rows that must be dropped, then Mysql will need to scan for a longer time compared to if almost all the rows are valid. In addition, you may find that the "density" of interesting rows is not constant throughout the range being scanned! If your application is paginating through a large data set, you may find that different pages have different query times, depending on how many rows need to be filtered out on each page.

# Join Algorithms
## Nested-Loop Join
The primary algorithm used by Mysql to join tables is a couple variations on "nested-loop". This a very straightforward algorithm:
```
for each row in tableA:
for each matching row in tableB:
send to output steram
```
Because Mysql is often capable of streaming joins, when the join query includes a `LIMIT x` the full join may not have to be executed:
1. Mysql executes query in the outer table
2. For the first row in the range, look-up matching rows in the inner table
3. For each matching row, emit to output stream
4. Stop execution if enough rows found, otherwise move to next row and goto 2
Note that similar to un-indexed row scans, this does not apply to all conditions (for example, if sorting is required the full dataset is required in memory).
## Hash Join
The hash-join algorithm avoids the N+1 B-tree traversal by taking some time upfront (`O(n)`) to build an in-memory hash table. The reason this strategy can give a performance improvement over nested-loop in some cases is because a hash table lookup has an average profile of `O(1)` compared to B-tree traversal at `O(logn)`. Given we may have to do this lookup many times (`m` times), the overall performance profile of hash-join is `O(n + m)`, whereas nested-loop's profile is `O(nlogm)`.
The below plot shows the region (shaded blue) where the function `n+m` has a lower value than `n*logm`:

The tradeoff is of course that this (potentially large) hash table must fit into memory. For this reason one strategy to improve hash-join performance is to limit the size of this temporary table by `SELECT`-ing only those columns which you really need (to reduce width), and pre-filtering as many rows as possible (to reduce height).
The second thing to keep in mind for performance of hash-joins is that indexes on the join condition will not be used. Rather, the place to focus is on indexing any independent filters if possible. For example, consider the following query:
```sql
SELECT * FROM tableA t1 JOIN tableB t2
ON t1.shared_id = t2.shared_id
WHERE t1.colA = "foo"
AND t2.colB = "bar"
```
The best indexes for this query given a hash-join would be on `t1.colA` and a second index on `t2.colB`. Execution of this join would then look like:
1. Use the index on `colA` to find all rows in t1 where `colA = "foo"`.
2. For each row, build a hash table where the key is `t1.shared_id` and the value is the row.
3. Use the index on `colB` to find all rows in t2 where `colB = "bar"`.
4. For each row, look up the matching t1 rows from the hash table by `t2.shared_id`
# Compound Cursor Iteration
In the [range-type queries section](#range-type-queries) I briefly introduced the problem of using an ID based cursor to paginate through a dataset queried via a range-type query. One potential solution to this problem is to use a *compound cursor*. To work, this cursor must be constructed from the column being filtered with the range. For example, lets consider the query `SELECT * FROM blog_posts WHERE blog_id=10 AND created_at>"2023-01-01"`. The natural index to use for this range query would be `[blog_id, created_at]`.
Because the range query filter is performed on the `created_at` column, I will propose a compound cursor of `created_at, id`. Let's take a look at how the query structure changes. The first query of our iteration will look something like this:
```sql
SELECT * FROM blog_posts
WHERE blog_id = 10 AND created_at > "2023-01-01"
ORDER BY created_at, id ASC
LIMIT 100
```
This will get the first "page" of 100 results. Notice that we are ordering by `created_at, id`, which is the natural ordering of the index. This allows mysql to efficiently grab the first 100 rows it sees without scanning the full time range.

Now lets look at how we get the next "page" of results. The "cursor value" is defined as the `created_at` and `id` values from the last row in the batch of 100 previously selected. We'll call these values `x` and `y` for simplicity.
```ruby
x = batch.last.created_at,
y = batch.last.id
```
The structure of the query that loads the second page of results has this form:
```sql
SELECT * FROM blog_posts
WHERE blog_id = 10
AND (
created_at = x AND id > y
OR created_at > x
)
ORDER BY created_at, id ASC
LIMIT 100
```
Notice in this query that we have an `OR` clause, meaning mysql is going to navigate the index **two times**, once per "side" of the clause. Lets consider these as two seperate queries for the sake of a performance analysis.
```sql
-- Query A: the "left" side of the OR clause
SELECT * FROM blog_posts
WHERE blog_id = 10 AND created_at = x AND id > y
ORDER BY created_at, id ASC
LIMIT 100
-- Query B: the "right" side of the OR clause
SELECT * FROM blog_posts
WHERE blog_id = 10 AND created_at > x
ORDER BY created_at, id ASC
LIMIT 100
```
By analysing the OR clauses piece-wise like this, we can now see that each clause has only **one** range filter. Combining this with the fact that the `ORDER BY` is the natural ordering of these indexes, we have solved both of the original problems! No more filesort, no more unsolvable double-range filters.

🟡 A note of warning: this pattern may only work as you expect for columns that have **immutable** values. Like any data structure iteration, if a value changes during your iteration your process may either process a row twice or not at all! For example, consider if instead of iterating on `created_at, id` we were iterating on `updated_at, id`. If a row is updated (and therefore `updated_at` _increases_) while a process is already iterating through the dataset, we may see that updated row twice: once with its lower `updated_at` value, and again with the higher value.
-

@ c2827524:5f45b2f7
2025-02-12 12:22:11
## L’animo umano

Una delle entità più belle che esistono e che, a mio parere, rendono ancor più meraviglioso questo mondo, è **l’animo degli esseri umani**. È un cocktail fatto di sentimenti, intenzioni, azioni e logica. Quelli che preferisco sono gli animi gentili.
Le azioni e le intenzioni devono convergere verso la delicatezza, senza una sbavatura, per essere gentili e io adoro la gentilezza, la riconosco al volo, forse perché non sono delicata. Per niente.
L’animo è forse **uno dei più grandi segreti dell’umanità**: in genere perché lo si tiene sempre privato, come è anche logico che sia.
C’è un solo fattore che fa rivelare l’animo alle persone, loro malgrado: uno stress test estremo.
Dal febbraio del 2020, lo stress test si è tramutato in un organismo multidimensionale, uscendo dalla fantasia distopica di George Orwell e – loro malgrado – **tutti hanno dovuto manifestare l’animo segreto**.
Fateci caso: è con il covid-1984 che avete scoperto la vera natura di amici, parenti, sconosciuti o conoscenti.
## Stato di eccezione

La distopia non è mica fuoriuscita da un laboratorio di Wuhan, che ha infettato un pangolino, che ha infettato una papera, che al mercato mio padre comprò. **Ha origini molto più antiche**.
Profondi conoscitori dell’animo umano, in grado di prevedere le reazioni delle masse di fronte ad ogni tipo di evento, potrebbero progettare modelli catastrofici e predeterminare con una precisione disarmante la risposta delle persone comuni. Ad esempio di fronte alla probabilità che quattro aerei impazziscano nei cieli americani di una splendida mattina di settembre, oppure guardando i corpi smembrati di un attentato compiuto da una qualunque “sigla” islamica.
Infine, potrebbero decidere come e quando dare una sferzata finale allo stress test, ad esempio con il pangolino. O era il pipistrello?
È la *«forma legale di ciò che non può avere forma legale»*, più in generale lo spirito disumano dei governanti di oggi, la consuetudine della guerra preventiva, la quale impone con forza che *«lo stato di eccezione tende sempre più a presentarsi come il paradigma di governo dominante della politica contemporanea»*.
Così analizza magistralmente Giorgio Agamben nel II° volume della raccolta Homo Sacer, intitolato per l’appunto [Stato di Eccezione](https://www.amazon.it/s?k=stato+di+eccezione+agamben&adgrpid=1234751876426057&hvadid=77172156923137&hvbmt=be&hvdev=c&hvlocphy=1861&hvnetw=s&hvqmt=e&hvtargid=kwd-77172234261086%3Aloc-93&hydadcr=18605_1867270&mcid=df58fe78258f374b81f1fd0eeaa1c659&msclkid=ea580711f461117b4cc160bdad34d584&tag=amamitsp-21&ref=pd_sl_7ni9dvsw1h_e).
## Stato indegno

Gli esseri umani, fondamentalmente miti e pacifici, tendono a condurre vite “normali” in ogni condizione ambientale.
Un’unica variabile tende ad interferire per cambiare la condizione ambientale: la politica dello stato. E **lo fa in maniera sempre negativa**.
Lo stato crea emergenze, per poi sbattere il suo (piccolissimo) pene sul tavolo e imporre con forza la soluzione, che tenderà puntualmente a facilitare la propria vita rendendo impossibile quella dei ~~cittadini~~ sudditi.
Le disuguaglianze create hanno poi **il solo scopo di mettere** esseri miti e pacifici (ma sotto costante pressione) **gli uni contro gli altri**.
Pensateci: da quanti decenni siete sotto la pressione di una *«forma legale di ciò che non può avere forma legale»*? Sentendo il Marchese del Grillo ***«Io so’ io, voi siete un cazzo»***, probabilmente è qualche secolo che questo stato indegno esiste.
## Vera natura o Nuda vita?

Il fatto, poi, che lo stato indegno venga accettato senza fiatare, fa parte di quella serie di reazioni delle masse e che i profondi conoscitori dell’animo umano sfruttano per mantenere il potere.
Si passa poi alle peggiori angherie che lo stato indegno e i suoi agenti perpetrano nei confronti dei ~~cittadini~~ sudditi, alle estreme disparità tra ~~cittadini~~ sudditi e i “servitori” dello stato, chiamati così perché servono lo stato indegno e non i ~~cittadini~~ sudditi.
Prima di arrivare alla sferzata finale dello stress test, persone miti e pacifiche hanno subito così tanti torti da non saperli più contare, ormai fanno parte della normalità. La loro esistenza è ormai ridotta a quello che Walter Benjamin prima e Giorgio Agamben poi definiscono la **Nuda Vita**, mettendo in analogia i sudditi con i detenuti di Guantanamo, giuridicamente innominabili e inclassificabili, ovvero ***«oggetto di una pura signoria di fatto»***.
## Il sontuoso master

Nello stato di eccezione in cui viviamo da almeno 50 anni, a parte pochi dotati di un immenso spirito di osservazione (e i profondi conoscitori al potere, chiaro), nessuno di noi ha mai avuto **veramente** il piacere di conoscere la reale natura delle persone con cui abbiamo scelto di circondarci.
Magari c’era quel “piccolo tarlo”, quella “vocina” che ci ha fatto preferire alcuni piuttosto che altri, ma alla fine ha sempre prevalso l’attitudine mite e pacifica, che ha messo a tacere quella vocina.
covid-1984 ha il merito di aver messo a nudo tutti: vittime e carnefici. Si tratta verosimilmente di **un sontuoso master che svelerà la vera natura di ognuno**, **nessuno escluso**. Ahinoi, il master è decennale e siamo appena all'inizio del V° anno accademico.
## Istruzioni, prima ancora che l’istruzione

Se c’è un consiglio che mi sento di dare a chi è ancora molto giovane, è proprio quello di non mettere mai a tacere quella “vocina”, per nessun motivo, seppure plausibile. Anche senza rovinare i rapporti, ma l’animo umano va sempre indagato, **si deve fare chiarezza sulla vera natura delle persone con cui si decide di fare un percorso di vita**.
La scoperta porterà ad evitare tutti quei “servitori” dello stato di cose indegno di essere definito umano. I *compliant*, gli asserviti, quelli senza spina dorsale o, peggio, **che hanno un interesse personale a mantenere lo status quo** devono essere evitati a tutti i costi.
È oltremodo doloroso, ma va fatto. Questi indegni devono essere isolati al più presto, in maniera da renderli innocui. Sono loro il vero esercito dello stato indegno, disposti a combattere qualunque guerra pur di rimediare un piccolissimo quanto ridicolo privilegio.
Oggi, i tempi in cui questo esercito si abbassava a tanto per il classico piatto di lenticchie riscaldate, sono un lontanissimo ricordo. covid-1984 ha ulteriormente abbattuto lo standard: ora gli indegni fiancheggiano qualsiasi assurdità **in cambio di un piatto di lenticchie rimasticate dalla signoria di fatto**.
L’unico risultato possibile è che l'infame stato rafforza il suo potere di controllo e rosicherà uno alla volta i (pochi) diritti e la libertà di chiunque.
Ecco perché bisogna spuntare le armi di questo spregevole stato di cose colpendo l’anello debole, isolandolo. Debole perché non ci crede (nello stato) ma agisce asservito solo per quel piatto di lenticchie (quelle rimasticate e sputate).
La prima volta che si incontrano, la vocina vi metterà di fronte alla sensazione di essere ai limiti di uno scontro frontale: capire da che parte andrà il rivale, per buttarsi in quella opposta ed evitare così uno schianto fatale.
Fatelo: buttatevi dall’altra parte. E scegliete la parte giusta.
-

@ a4a6b584:1e05b95b
2025-01-02 18:13:31
## The Four-Layer Framework
### Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
**Example**: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- **Tip**: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
_Once you have the big picture in mind, it’s time to start breaking it down._
---
### Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
**Example**: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- **Tip**: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
_With your categories in place, you’re ready to dive into the details that bring them to life._
---
### Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
**Example**: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- **Tip**: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
_Now that you’ve mastered the essentials, you can expand your knowledge to include extra material._
---
### Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
**Example**: Learn about rare programming quirks or historical trivia about a language’s development.
- **Tip**: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
---
## Pro Tips for Better Learning
### 1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
### 2. Map It Out
Create visual aids like [diagrams or concept maps](https://excalidraw.com/) to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
### 3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching **exposes any gaps** in your understanding and **helps reinforce** the material.
### 4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to **explore your topic** in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.
**Tip**: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
---
## Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-

@ 575a8227:065bba95
2025-02-12 10:57:10
https://www.youtube.com/watch?v=SiV7UhoiZM8
Hola nostr,
El reciente podcast de lunaticoin con Salinas ha puesto sobre la mesa una reflexión profunda sobre el llamado "fondo estratégico Bitcoin" de Trump, revelando una paradoja que merece nuestra atención.
Pensemos en el camino que hemos recorrido como individuos en el ecosistema Bitcoin. Durante años, cada uno de nosotros ha trabajado incansablemente, ahorrando con determinación para adquirir Bitcoin con dinero real, fruto de nuestro esfuerzo diario. En ese trayecto, hemos enfrentado críticas constantes: que si Bitcoin solo servía para actividades ilícitas, que si era un esquema Ponzi, que si carecía de valor intrínseco.
Ahora, en 2025, presenciamos un giro narrativo sorprendente. Los mismos que demonizaron Bitcoin proponen crear un "fondo estratégico", ¿y cómo planean financiarlo? Con la misma herramienta contra la que Bitcoin nació para protegernos: la impresión infinita de dinero fiat. Pretenden adquirir con papel sin respaldo lo que a tantos nos ha costado años de esfuerzo y convicción conseguir.
La comunidad Bitcoin se ha construido desde abajo, con personas que creyeron en el proyecto cuando pocos lo hacían, que mantuvieron sus convicciones en los momentos más difíciles, que construyeron infraestructura y educaron a otros. Somos nosotros, no los oportunistas de última hora, quienes hemos llevado Bitcoin hasta donde está hoy.
La propuesta actual representa una doble expropiación: primero devalúan nuestros ahorros mediante la inflación, y luego utilizan ese mismo dinero devaluado para intentar acaparar Bitcoin. Es un mecanismo que perpetúa exactamente aquello contra lo que Bitcoin fue creado para luchar.
Bitcoin nació como una herramienta de libertad financiera para el individuo, no como un instrumento más de control centralizado. Cada día que pasa, se hace más evidente que ningún político, independientemente de su retórica, representa los valores fundamentales de Bitcoin.
En estos momentos, mantener nuestros sats no es solo una decisión financiera, es una declaración de principios.
HODL 🟠₿
 @ 7d33ba57:1b82db35
2025-02-14 01:46:37The short answer is YES—but the more honest answer is that it’s much harder than when I started. I’ve been in the travel stock media industry for over 13 years, creating a vast archive of stock photos and videos from around the world. You can check out my portfolio on [https://www.shutterstock.com/g/traveltelly](Shutterstock). My work is also available on Pond5, Videoblocks, and Adobe Stock. Other big agencies where I don’t have my media are Getty Images and iStock. My media has been featured on TV channels and even in feature films. However, most of the time, contributors don’t know exactly where their content is used—stock agencies (the middlemen) keep that information to themselves. While stock media can still generate income, it requires persistence, a large portfolio, and an understanding of the ever-changing market. When I started filming stock footage, most people didn’t even have a phone capable of taking good photos or videos—can you imagine? Now, everyone is a (travel) content creator. Technology has evolved, but creating a well-composed photo or video is still an art. However, the combination of improved tech and the increasing centralization of the stock media market has made it much harder to earn a decent income from stock media compared to 10 years ago.  **Centralization & Declining Royalties** Over the years, I’ve watched stock media royalties decline year after year. In the beginning, I couldn't understand why I wasn’t able to recoup the cost of my expensive camera—one I specifically bought to shoot high-quality 4K footage. As the stock media industry became more centralized, agencies took a larger cut while contributors earned less, despite creating higher-quality content. The market became saturated, and with more competition and lower payouts, making a sustainable income from stock media became increasingly difficult.  **The Reality of Centralization in Stock Media** Every year, stock agencies announced yet another royalty downgrade for contributors. They always framed it as something beneficial for content creators, but in reality, it only served the big companies and their shareholders. As content creators, we had no say in the matter. These agencies grew too big and powerful, and they knew it. Leaving one platform wasn’t really an option—doing so would only mean an even greater loss of income. In recent years, the industry has become even more centralized, with only a handful of major agencies buying out smaller competitors. This consolidation further reduces competition, giving contributors even less control over pricing, royalties, and where their content is used.  **The Bitcoin Standard: A Wake-Up Call** I couldn’t understand why I was struggling to pay off my expensive camera investment, despite working hard and producing high-quality content. Until then, I had never really thought about how money worked. That changed in 2018 when I read The Bitcoin Standard—an absolute eye-opener. That book sparked my curiosity about Bitcoin. Like many, I initially got distracted by shitcoins, thinking I could multiply my holdings faster—after all, Bitcoin seemed “too expensive.” It was a hard but valuable lesson. Just like in a casino, you can win and lose a lot with altcoins, but that has nothing to do with Bitcoin itself. After those first few years of learning, I realized that for me, Bitcoin—not crypto—was the only way forward.  **From Centralization to Decentralization** When people ask me if they should start selling stock footage, my answer is always the same: It’s much harder now than when I started. Sure, you can make a few bucks, but is all the time and effort really worth it? If I had to start today, I simply wouldn’t—it’s way more work than what you’ll earn. Instead of spending years building content for centralized platforms that take the biggest cut, I believe it’s better to focus on decentralized media like Nostr. In my opinion, that’s where the future lies.  Nostr: A New Protocol for Socializing (and More) Nostr is a revolutionary protocol that goes beyond just social networking. You can read all about it at [Nostr.org](Nostr.org). As a content creator, one of the most exciting aspects of Nostr is the ability to earn directly through Zaps—small payments made in Satoshis (the smallest unit of Bitcoin). * 1 Bitcoin = 100 million Satoshis * By receiving Zaps, you’re not just earning—you’re stacking the hardest money (Bitcoin) directly on Nostr. This shift toward decentralized earning is a game changer, giving creators more control and financial sovereignty compared to traditional, centralized platforms.  **Join Nostr and Create Your Freedom Content** On Nostr, no one can stop you. No one can deplatform you. You can be truly free.Whether you're a content creator, artist, or thinker, Nostr empowers you to share your work without censorship or gatekeepers. It’s a place where you control your content, connect directly with your audience, and even earn Bitcoin through Zaps.Embrace decentralization. ***Join Nostr and take back your freedom*** 🚀
@ 7d33ba57:1b82db35
2025-02-14 01:46:37The short answer is YES—but the more honest answer is that it’s much harder than when I started. I’ve been in the travel stock media industry for over 13 years, creating a vast archive of stock photos and videos from around the world. You can check out my portfolio on [https://www.shutterstock.com/g/traveltelly](Shutterstock). My work is also available on Pond5, Videoblocks, and Adobe Stock. Other big agencies where I don’t have my media are Getty Images and iStock. My media has been featured on TV channels and even in feature films. However, most of the time, contributors don’t know exactly where their content is used—stock agencies (the middlemen) keep that information to themselves. While stock media can still generate income, it requires persistence, a large portfolio, and an understanding of the ever-changing market. When I started filming stock footage, most people didn’t even have a phone capable of taking good photos or videos—can you imagine? Now, everyone is a (travel) content creator. Technology has evolved, but creating a well-composed photo or video is still an art. However, the combination of improved tech and the increasing centralization of the stock media market has made it much harder to earn a decent income from stock media compared to 10 years ago.  **Centralization & Declining Royalties** Over the years, I’ve watched stock media royalties decline year after year. In the beginning, I couldn't understand why I wasn’t able to recoup the cost of my expensive camera—one I specifically bought to shoot high-quality 4K footage. As the stock media industry became more centralized, agencies took a larger cut while contributors earned less, despite creating higher-quality content. The market became saturated, and with more competition and lower payouts, making a sustainable income from stock media became increasingly difficult.  **The Reality of Centralization in Stock Media** Every year, stock agencies announced yet another royalty downgrade for contributors. They always framed it as something beneficial for content creators, but in reality, it only served the big companies and their shareholders. As content creators, we had no say in the matter. These agencies grew too big and powerful, and they knew it. Leaving one platform wasn’t really an option—doing so would only mean an even greater loss of income. In recent years, the industry has become even more centralized, with only a handful of major agencies buying out smaller competitors. This consolidation further reduces competition, giving contributors even less control over pricing, royalties, and where their content is used.  **The Bitcoin Standard: A Wake-Up Call** I couldn’t understand why I was struggling to pay off my expensive camera investment, despite working hard and producing high-quality content. Until then, I had never really thought about how money worked. That changed in 2018 when I read The Bitcoin Standard—an absolute eye-opener. That book sparked my curiosity about Bitcoin. Like many, I initially got distracted by shitcoins, thinking I could multiply my holdings faster—after all, Bitcoin seemed “too expensive.” It was a hard but valuable lesson. Just like in a casino, you can win and lose a lot with altcoins, but that has nothing to do with Bitcoin itself. After those first few years of learning, I realized that for me, Bitcoin—not crypto—was the only way forward.  **From Centralization to Decentralization** When people ask me if they should start selling stock footage, my answer is always the same: It’s much harder now than when I started. Sure, you can make a few bucks, but is all the time and effort really worth it? If I had to start today, I simply wouldn’t—it’s way more work than what you’ll earn. Instead of spending years building content for centralized platforms that take the biggest cut, I believe it’s better to focus on decentralized media like Nostr. In my opinion, that’s where the future lies.  Nostr: A New Protocol for Socializing (and More) Nostr is a revolutionary protocol that goes beyond just social networking. You can read all about it at [Nostr.org](Nostr.org). As a content creator, one of the most exciting aspects of Nostr is the ability to earn directly through Zaps—small payments made in Satoshis (the smallest unit of Bitcoin). * 1 Bitcoin = 100 million Satoshis * By receiving Zaps, you’re not just earning—you’re stacking the hardest money (Bitcoin) directly on Nostr. This shift toward decentralized earning is a game changer, giving creators more control and financial sovereignty compared to traditional, centralized platforms.  **Join Nostr and Create Your Freedom Content** On Nostr, no one can stop you. No one can deplatform you. You can be truly free.Whether you're a content creator, artist, or thinker, Nostr empowers you to share your work without censorship or gatekeepers. It’s a place where you control your content, connect directly with your audience, and even earn Bitcoin through Zaps.Embrace decentralization. ***Join Nostr and take back your freedom*** 🚀 @ 85bdb587:7339d672
2025-02-13 22:56:08## Marty's Bent I must admit, I have been thoroughly impressed with the work the Trump administration has done since taking the reins from the Biden admin 23 days ago. Over the course of the first eight years of this newsletter there were multiple books-worth of words written about the rampant government corruption in the United States and the negative effects it was having on the economy, freedom and the psyche of the American people. The emergence of DOGE, its rag-tag team of autistic Gen Z'ers and the blatant fraud that has been surfaced is equally gratifying and infuriating. For the longest time any American taxpayer with the smallest shred of common sense has known that they've been getting screwed by the federal government. We've said it for many years; taxes are a humiliation ritual in which the Common Man works his ass off for a meager wage, the government takes one third of it, and then lines their own pockets. We were reaching levels of corruption that rivaled Soviet Russia. *“We know that they are lying, they know that they are lying, they even know that we know they are lying, we also know that they know we know they are lying too, they of course know that we certainly know they know we know they are lying too as well, but they are still lying. In our country, the lie has become not just moral category, but the pillar industry of this country.”* - Aleksandr Solzhenitsyn The fact that all of the corruption that has been building up for decades in the United States is being brought to the light is extremely encouraging. We're not out of the woods yet, but it looks like we're actually making material progress to unveil the parasites in Washington DC. Hopefully DOGE's actions will lead to their eradication from American politics and a shrinking of the federal government to its smallest viable form. Nothing proves that DOGE is over the target more than the pearl clutching and screeching that is coming from the halls of Congress. FEED ME the crocodile tears of Elizabeth Warren, Maxine Waters and Mitch McConnell. These people are criminals and deserve nothing but the utmost contempt from the American people. The louder the screams coming from these individuals and others in similar positions should only be seen as confirmation that they are scared and are attempting to evade justice by screaming "CoNsTiTuTiOnAl CrIsIs" as many times as is humanly possible. With all of that being said, DOGE should be seen as a mechanism to identify corruption, root it out, and salvage what they can of the American taxpayers' money. It's an admirable endeavor that should be lauded, but it only goes so far. Unfortunately for the United States, you can't DOGE the debt. via TFTC 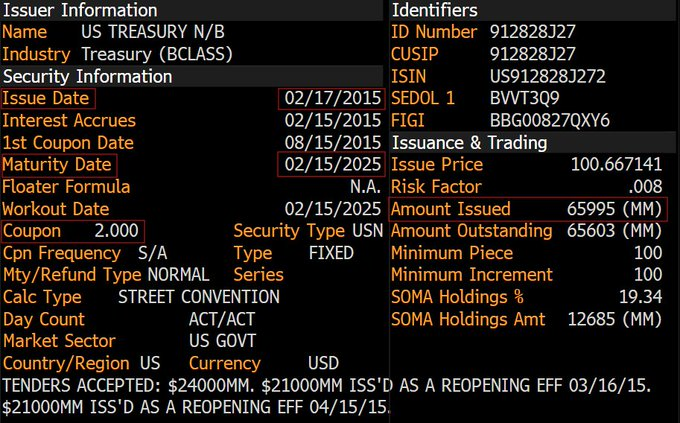 What you are looking at is a block of 10-year US Treasuries that need to be rolled over in a couple of days. Particularly, $66B 10Ys that were issued in February 2015 when interest rates were 2.00%. They'll be rolling over in a few days at 4.55%, representing an additional $1.67B in interest expense on the debt per year. While that may not seem a lot in a world where governments and central banks throw trillions around like their going out of style, it is important to realize that this is just one block of bonds that needs to be rolled over this year. If my memory serves me correctly, the Treasury needs to roll over ~$6 TRILLION in debt in the first half of this year. Using some back of the napkin Marty math skills, if all that debt rolled over at the same interest rate, that would add another ~$150B to the annual expense we pay on the interest on that debt. And in case you missed it, earlier this week the United States surpassed an incredible milestone; we are now paying $100B a MONTH in interest expense on the debt and $1.2T per year. If all of the debt that needs to be rolled over in the first half of the year is rolled over where interest rates stand today, it will increase the annual debt expense by more than 10%. Not great, Bob! 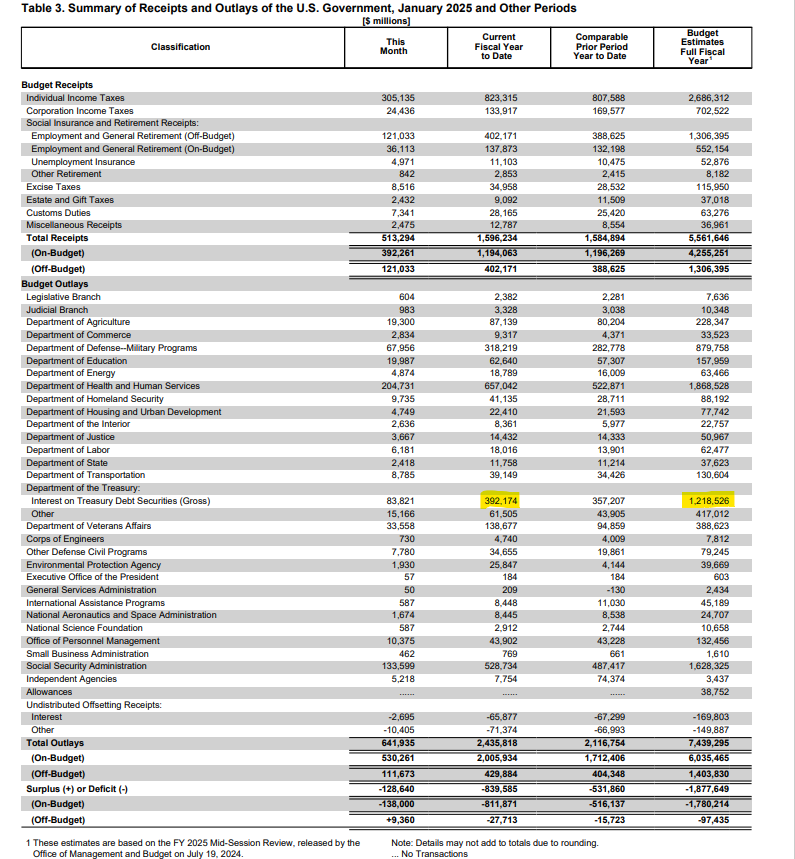 The actions of DOGE are incredible to see, but you simply can't eliminate debt that has already been accrued by raiding the Treasury and ousting corrupt bureaucrats. The United States has an obligation to pay back those who hold our debt and the only way to do that is to produce a surplus that allows the government to pay down what has been accrued or issue new debt at wherever rates find themselves at the time of roll over to pay it back. While spending cuts are being made we, unfortunately do not find ourselves reaping the benefits of a government surplus at the moment, so we'll have to roll over the debt. With interest rates where they are, the increase on the debt expense may put the United States government in a position where it becomes impossible to take care of the debt issue without printing their way out of it or getting all of the world's leaders around the table for a Bretton Woods-like monetary reset. We'll see how it plays out. One thing I know for damn sure is that no matter how the US decides to deal with the debt issue, bitcoin is going to benefit massively. If they print their way out people are going to flee to scarce assets, and bitcoin is the scarcest asset on the planet outside of time. If they reset the monetary order people are going to flee to bitcoin due to the certainty of its monetary policy and its relative inability to be corrupted. Now for... ## An Incredibly Simple Yet Powerful Quote As discussed in my recent conversation with Porter Stansberry, the mounting U.S. government debt problem has created an intriguing dynamic for Bitcoin holders. Porter articulated a compelling perspective: government debt, which threatens most people's savings and financial security, actually becomes an asset for Bitcoin owners. The logic is straightforward – as debt levels become unsustainable, more people will be forced to flee the traditional financial system, driving demand for alternative stores of value like Bitcoin. *"Their debt is your problem until you own Bitcoin. And then the moment you own bitcoin their debt is your greatest asset."* - Porter Stansberry This thesis becomes even more relevant when considering the staggering numbers we discussed. The U.S. currently faces $37 trillion in on-balance-sheet debt, plus an additional $190 trillion in unfunded liabilities from Medicare, Medicaid, and Social Security. These obligations, as Porter and I agreed, are mathematically impossible to fulfill without significant monetary debasement. This reality creates a powerful tailwind for Bitcoin adoption, as it positions the asset as one of the few viable escape hatches from a system drowning in debt. [Check out the full podcast](https://www.youtube.com/watch?v=2f8LWO_RmtU&ab_channel=TFTC) here for more on Trump's economic strategy, the commercial real estate crisis, and the future of energy markets in America. ## Headlines of the Day Bitcoin's Realized Cap Reaches Record High - via [X](https://x.com/TFTC21/status/1889831485701833056) Texas Bill Removes $500M Cap on State Bitcoin Purchases - via [X](https://x.com/BitcoinPierre/status/1889821134021075012) ETF Demand Outpaces Mining Production - via [X](https://x.com/TFTC21/status/1889779939982840185) U.S. Interest Expense on the National Debt Hits $1.2T - via [X](https://x.com/TFTC21/status/1889764204208324764) ## Bitcoin Lesson of the Day Bitcoin transactions work by sending entire "outputs" (batches of bitcoin) rather than spending partial amounts. When spending bitcoin, the entire output must be used and split into new outputs. For example, if you have a 25 BTC output and want to spend 1 BTC, you'd create two new outputs: 1 BTC to the recipient and 24 BTC back to yourself as change. The original 25 BTC output becomes spent and unusable. When making a payment that exceeds any single output you own, multiple outputs can be combined as inputs in a transaction. For instance, to spend 4.2 BTC, you might combine outputs of 1 + 0.5 + 2 + 1 BTC as inputs, creating new outputs of 4.2 BTC (payment) and 0.3 BTC (change). Transaction fees are created by making the total output amount slightly less than the input amount. The difference becomes the fee, which miners collect when including the transaction in a block. The balance of a bitcoin address is the sum of all its unspent transaction outputs (UTXOs). [Outputs | What is a Transaction Output? A simple explanation of transaction outputs and how they work.](https://learnmeabitcoin.com/beginners/guide/outputs/) ICYMI Fold opened the waiting list for the new Bitcoin Rewards Credit Card. Fold cardholders will get unlimited 2% cash back in sats. [Get on the waiting list](https://foldapp.com/credit-card?r=BgwRS) now before it fills up! $200k worth of prizes are up for grabs. Ten31, the largest bitcoin-focused investor, has deployed $150M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at [ten31.vc/funds](ten31.vc/funds).
@ 85bdb587:7339d672
2025-02-13 22:56:08## Marty's Bent I must admit, I have been thoroughly impressed with the work the Trump administration has done since taking the reins from the Biden admin 23 days ago. Over the course of the first eight years of this newsletter there were multiple books-worth of words written about the rampant government corruption in the United States and the negative effects it was having on the economy, freedom and the psyche of the American people. The emergence of DOGE, its rag-tag team of autistic Gen Z'ers and the blatant fraud that has been surfaced is equally gratifying and infuriating. For the longest time any American taxpayer with the smallest shred of common sense has known that they've been getting screwed by the federal government. We've said it for many years; taxes are a humiliation ritual in which the Common Man works his ass off for a meager wage, the government takes one third of it, and then lines their own pockets. We were reaching levels of corruption that rivaled Soviet Russia. *“We know that they are lying, they know that they are lying, they even know that we know they are lying, we also know that they know we know they are lying too, they of course know that we certainly know they know we know they are lying too as well, but they are still lying. In our country, the lie has become not just moral category, but the pillar industry of this country.”* - Aleksandr Solzhenitsyn The fact that all of the corruption that has been building up for decades in the United States is being brought to the light is extremely encouraging. We're not out of the woods yet, but it looks like we're actually making material progress to unveil the parasites in Washington DC. Hopefully DOGE's actions will lead to their eradication from American politics and a shrinking of the federal government to its smallest viable form. Nothing proves that DOGE is over the target more than the pearl clutching and screeching that is coming from the halls of Congress. FEED ME the crocodile tears of Elizabeth Warren, Maxine Waters and Mitch McConnell. These people are criminals and deserve nothing but the utmost contempt from the American people. The louder the screams coming from these individuals and others in similar positions should only be seen as confirmation that they are scared and are attempting to evade justice by screaming "CoNsTiTuTiOnAl CrIsIs" as many times as is humanly possible. With all of that being said, DOGE should be seen as a mechanism to identify corruption, root it out, and salvage what they can of the American taxpayers' money. It's an admirable endeavor that should be lauded, but it only goes so far. Unfortunately for the United States, you can't DOGE the debt. via TFTC 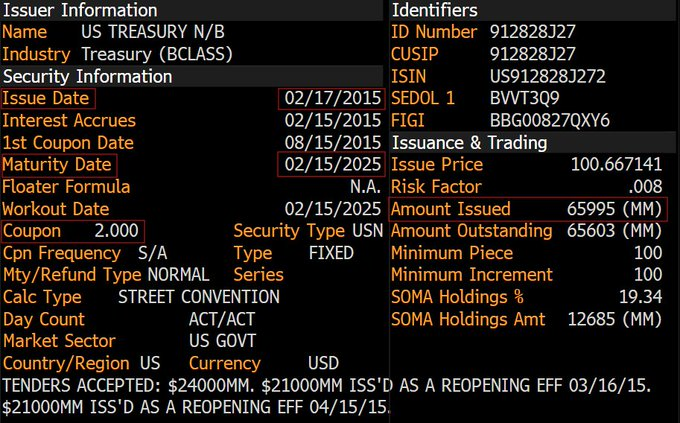 What you are looking at is a block of 10-year US Treasuries that need to be rolled over in a couple of days. Particularly, $66B 10Ys that were issued in February 2015 when interest rates were 2.00%. They'll be rolling over in a few days at 4.55%, representing an additional $1.67B in interest expense on the debt per year. While that may not seem a lot in a world where governments and central banks throw trillions around like their going out of style, it is important to realize that this is just one block of bonds that needs to be rolled over this year. If my memory serves me correctly, the Treasury needs to roll over ~$6 TRILLION in debt in the first half of this year. Using some back of the napkin Marty math skills, if all that debt rolled over at the same interest rate, that would add another ~$150B to the annual expense we pay on the interest on that debt. And in case you missed it, earlier this week the United States surpassed an incredible milestone; we are now paying $100B a MONTH in interest expense on the debt and $1.2T per year. If all of the debt that needs to be rolled over in the first half of the year is rolled over where interest rates stand today, it will increase the annual debt expense by more than 10%. Not great, Bob! 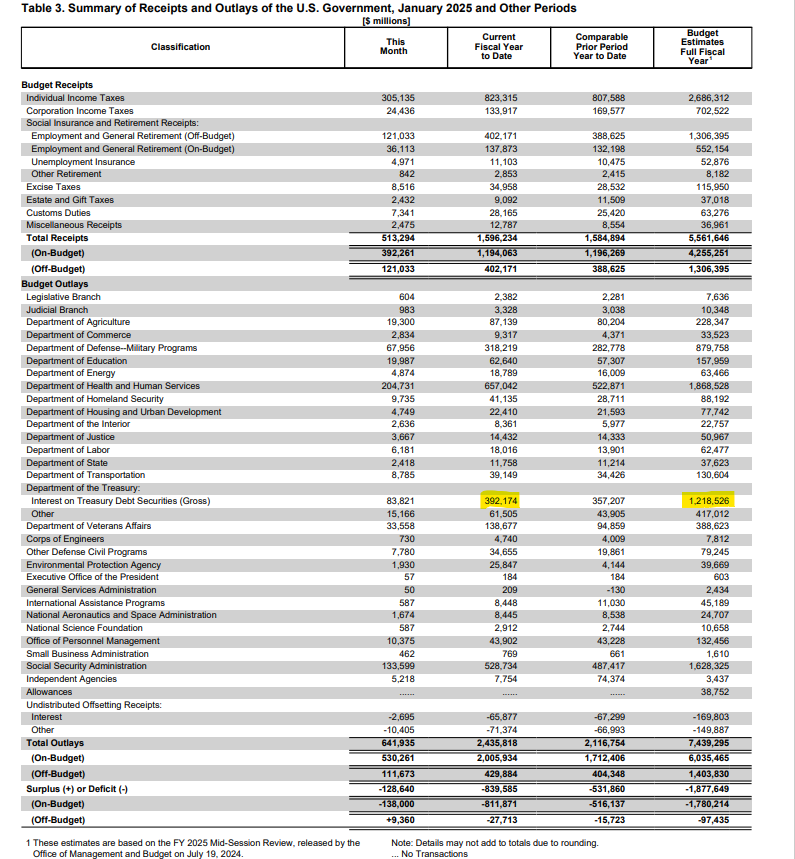 The actions of DOGE are incredible to see, but you simply can't eliminate debt that has already been accrued by raiding the Treasury and ousting corrupt bureaucrats. The United States has an obligation to pay back those who hold our debt and the only way to do that is to produce a surplus that allows the government to pay down what has been accrued or issue new debt at wherever rates find themselves at the time of roll over to pay it back. While spending cuts are being made we, unfortunately do not find ourselves reaping the benefits of a government surplus at the moment, so we'll have to roll over the debt. With interest rates where they are, the increase on the debt expense may put the United States government in a position where it becomes impossible to take care of the debt issue without printing their way out of it or getting all of the world's leaders around the table for a Bretton Woods-like monetary reset. We'll see how it plays out. One thing I know for damn sure is that no matter how the US decides to deal with the debt issue, bitcoin is going to benefit massively. If they print their way out people are going to flee to scarce assets, and bitcoin is the scarcest asset on the planet outside of time. If they reset the monetary order people are going to flee to bitcoin due to the certainty of its monetary policy and its relative inability to be corrupted. Now for... ## An Incredibly Simple Yet Powerful Quote As discussed in my recent conversation with Porter Stansberry, the mounting U.S. government debt problem has created an intriguing dynamic for Bitcoin holders. Porter articulated a compelling perspective: government debt, which threatens most people's savings and financial security, actually becomes an asset for Bitcoin owners. The logic is straightforward – as debt levels become unsustainable, more people will be forced to flee the traditional financial system, driving demand for alternative stores of value like Bitcoin. *"Their debt is your problem until you own Bitcoin. And then the moment you own bitcoin their debt is your greatest asset."* - Porter Stansberry This thesis becomes even more relevant when considering the staggering numbers we discussed. The U.S. currently faces $37 trillion in on-balance-sheet debt, plus an additional $190 trillion in unfunded liabilities from Medicare, Medicaid, and Social Security. These obligations, as Porter and I agreed, are mathematically impossible to fulfill without significant monetary debasement. This reality creates a powerful tailwind for Bitcoin adoption, as it positions the asset as one of the few viable escape hatches from a system drowning in debt. [Check out the full podcast](https://www.youtube.com/watch?v=2f8LWO_RmtU&ab_channel=TFTC) here for more on Trump's economic strategy, the commercial real estate crisis, and the future of energy markets in America. ## Headlines of the Day Bitcoin's Realized Cap Reaches Record High - via [X](https://x.com/TFTC21/status/1889831485701833056) Texas Bill Removes $500M Cap on State Bitcoin Purchases - via [X](https://x.com/BitcoinPierre/status/1889821134021075012) ETF Demand Outpaces Mining Production - via [X](https://x.com/TFTC21/status/1889779939982840185) U.S. Interest Expense on the National Debt Hits $1.2T - via [X](https://x.com/TFTC21/status/1889764204208324764) ## Bitcoin Lesson of the Day Bitcoin transactions work by sending entire "outputs" (batches of bitcoin) rather than spending partial amounts. When spending bitcoin, the entire output must be used and split into new outputs. For example, if you have a 25 BTC output and want to spend 1 BTC, you'd create two new outputs: 1 BTC to the recipient and 24 BTC back to yourself as change. The original 25 BTC output becomes spent and unusable. When making a payment that exceeds any single output you own, multiple outputs can be combined as inputs in a transaction. For instance, to spend 4.2 BTC, you might combine outputs of 1 + 0.5 + 2 + 1 BTC as inputs, creating new outputs of 4.2 BTC (payment) and 0.3 BTC (change). Transaction fees are created by making the total output amount slightly less than the input amount. The difference becomes the fee, which miners collect when including the transaction in a block. The balance of a bitcoin address is the sum of all its unspent transaction outputs (UTXOs). [Outputs | What is a Transaction Output? A simple explanation of transaction outputs and how they work.](https://learnmeabitcoin.com/beginners/guide/outputs/) ICYMI Fold opened the waiting list for the new Bitcoin Rewards Credit Card. Fold cardholders will get unlimited 2% cash back in sats. [Get on the waiting list](https://foldapp.com/credit-card?r=BgwRS) now before it fills up! $200k worth of prizes are up for grabs. Ten31, the largest bitcoin-focused investor, has deployed $150M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at [ten31.vc/funds](ten31.vc/funds). @ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get [this line](https://www.youtube.com/shorts/kqsomjpz7ok): “Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.” Yesterday, I came across a comment on the song [Devil Went Down to Georgia](https://youtu.be/ut8UqFlWdDc) that had a very similar feel to it:  America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans. That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form. For most countries, saying “our nation is the greatest” *is*, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people *should* be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence. But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America. That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is *freedom*. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit. American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are *definitionally* better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.) In *Devil Went Down to Georgia*, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.” *Libertas magnitudo est*
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get [this line](https://www.youtube.com/shorts/kqsomjpz7ok): “Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.” Yesterday, I came across a comment on the song [Devil Went Down to Georgia](https://youtu.be/ut8UqFlWdDc) that had a very similar feel to it:  America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans. That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form. For most countries, saying “our nation is the greatest” *is*, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people *should* be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence. But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America. That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is *freedom*. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit. American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are *definitionally* better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.) In *Devil Went Down to Georgia*, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.” *Libertas magnitudo est* @ e373ca41:b82abcc5
2025-02-13 22:27:58*This article has been written with the* ***[Pareto client](https://pareto.space/read).*** *(read it there for the full experience). It was first published in German by Milosz Matuschek on* ***["Freischwebende Intelligenz".](https://www.freischwebende-intelligenz.org/p/unterwanderter-journalismus-der-mediale)*** *** It is unmistakable. The hydra of the Deep State is losing a few heads - and this time it's the turn of the media heads. Anyone can look at [USASpending](https://www.usaspending.gov/) to see how much taxpayers' money has gone to whom in the USA. ### When the state pays its advocates The mainstream media were also among the beneficiaries: Politico (100% Axel Springer) received over [USD 7 million](https://www.usaspending.gov/recipient/fa0cefae-7cfb-881d-29c3-1bd39cc6a49e-C/latest); the New York Times received over USD 40 million. Thousands of (probably not always necessary) government subscriptions flowed to large media houses - paid for with taxpayers' money. A form of covert press financing by the state. At what point can or should we speak of state media? ") However, this is only the tip of the iceberg. The CIA front organization USAID ([known for its funding of virus research in Wuhan and other questionable activities](https://pareto.space/a/naddr1qqxnzden8quryveexq6rywp3qgswxu72gyq7ykjdfl9j556887jpzwu3mw3v9ez36quas55whq4te3grqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsz9nhwden5te0wfjkccte9ehx7um5wghxyctwvszsxfjh)) - [pumped USD 472.6 million directly into the media landscape via the “Internews Network”.](https://www.zerohedge.com/political/usaid-funded-massive-global-state-propaganda-news-matrix-nearly-billion-people-reach) FAZ journalist Udo Ulfkotte once called this “bought journalists” in a very clear and media-effective way, which was not good for his health. There is ample evidence of the CIA-USAID connections, for example [here](https://timesofindia.indiatimes.com/toi-plus/international/how-usaid-worked-alongside-cia-in-vietnam-a-whistleblowers-account/articleshow/118164225.cms), [here](https://foreignpolicy.com/2014/04/03/cuban-twitter-and-other-times-usaid-pretended-to-be-an-intelligence-agency/) and [here.](https://www.jstor.org/stable/4017728) ") But this is now over for the time being: USD 268 million, which was to go to “independent media for the free flow of information” (according to the [Columbia Journalism Review](https://www.cjr.org/the_media_today/usaid-and-the-media-in-a-time-of-monsters.php)) in 2025, has been frozen. The largest media influence machine in the Western world is bleeding a little. One has to admit: part of the media-deepstate swamp is actually being drained dry financially. The fact that the Columbia Journalism Review doesn't even seem to notice that “free international journalism”, which, as it writes, is largely funded by USAID, ceases to be “free journalism” speaks volumes about this “hotbed of journalism”. Matt Taibbi of Racket News rightly finds, “The legacy media system is dead. They just don't know it yet.” *** ADVERTISEMENT: *Looking for the easiest way to buy Bitcoin and store it yourself? The **[Relai app](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. **[Here you can buy Bitcoin](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.*  *Need more security? The **[Trezor wallets](https://trezor.io/trezor-safe-5-bitcoin-only?transaction_id=102e192a206d1585e56a2fddef6d83\&offer_id=238\&affiliate_id=35234)** are recommended and easy to use, others are available in the **[store](https://trezor.io/?transaction_id=102bc85bdca2733287749c7f879ebd\&offer_id=133\&affiliate_id=35234)**. Need more advice? Book an **[introductory meeting](https://trezor.io/trezor-expert-session?transaction_id=1020e18dad0aa4b1186289fd22e90f\&offer_id=241\&affiliate_id=35234)** with a wallet expert.* *** Large-scale media manipulation has become visible. The propaganda matrix, if you will. The disastrous thing about it: if the Overton window is infiltrated, so to speak, the entire institution of journalism cannot be trusted. Every day, readers must expect to be pulled through the nose ring of intelligence service narratives and public agendas by mainstream journalists who pretend to be objective (and are often simply clueless and unsuspecting). The panorama of what we are supposed to see and believe, so to speak. How many mainstream journalists today are basically mouthpieces for the services? Every mainstream reader must now ask themselves: Is my favorite journalist at NZZ, Welt, SZ, ZEIT or FAZ perhaps just a CIA-IM? There were no major dissenters among them: EU criticism? Vaccination criticism? Criticism of NATO? Criticism of Biden and America? Criticism of Nord Stream? There were brief moments on television when questions about journalists' ties to lobby organizations were still part of the German satire program. <https://x.com/Spitze_Zunge_/status/1887915509988876786> ### The cards in the media are being reshuffled The watchdog of the powerful has been infiltrated by the powerful. This means that the Fourth Power is not a power at all, but part of the executive branch, a mouthpiece of the government. The claim that the mainstream is quality journalism, the gold standard for trustworthy information, is therefore the real fake news. It is the last, now crumbling dogma of an infiltrated press sect that has formed a cartel and is subjecting citizens to a permanent psy-op with intelligence-controlled taxpayers' money. A troupe of spokespeople at the work of mental synchronization. <https://x.com/TopherField/status/1887962959072149989> ### The fight against independent media But they not only give to one, they also take from the other. While government agencies use taxpayers' money to promote a certain type of journalism, the juice is actively being cut off from the critical part. All it takes is to be classified as a “PEP” (politically exposed person) and the bank account is gone. This is what has just happened to swiss Radio Kontrafunk. The critical Swiss author Stefan Millius was canceled by his publisher. Others have had their monetization via YouTube cut off (Snicklink). Others are harassed by the state media authority (Multipolar, Alexander Wallasch). The next one has a house search. It has been known since the Twitter files that the government and services also intervened massively in social media communication. This is no longer the Cold War. But it is the cold information war. <https://www.youtube.com/watch?v=kmgWAGDFCZI> Is this all so outrageous and new? During the Cold War, the CIA systematically infiltrated media outlets in the US. Thousands of agents were deployed as journalists - and wrote what they were told. This “Operation Mockingbird”, which the Church Committee also investigated, never ended, so to speak. It lives on as Operation Mockingbird 2.0. Intelligence payments to media outlets continue to exist. USAID distributes millions for “pro-democratic” reporting. Government subscriptions keep uncritical media alive. Media control of public opinion is the most important tool of power in a modern “democracy”. The difference to back then? Today, the manipulation is global. However, these revelations come at a time when trust in the media is already at an all-time low. [The fear of being lied to by the powerful is currently the majority opinion at 70%.](https://www.edelman.com/trust/2025/trust-barometer) They are currently in the process of convincing the remaining 30% of their own incompetence. 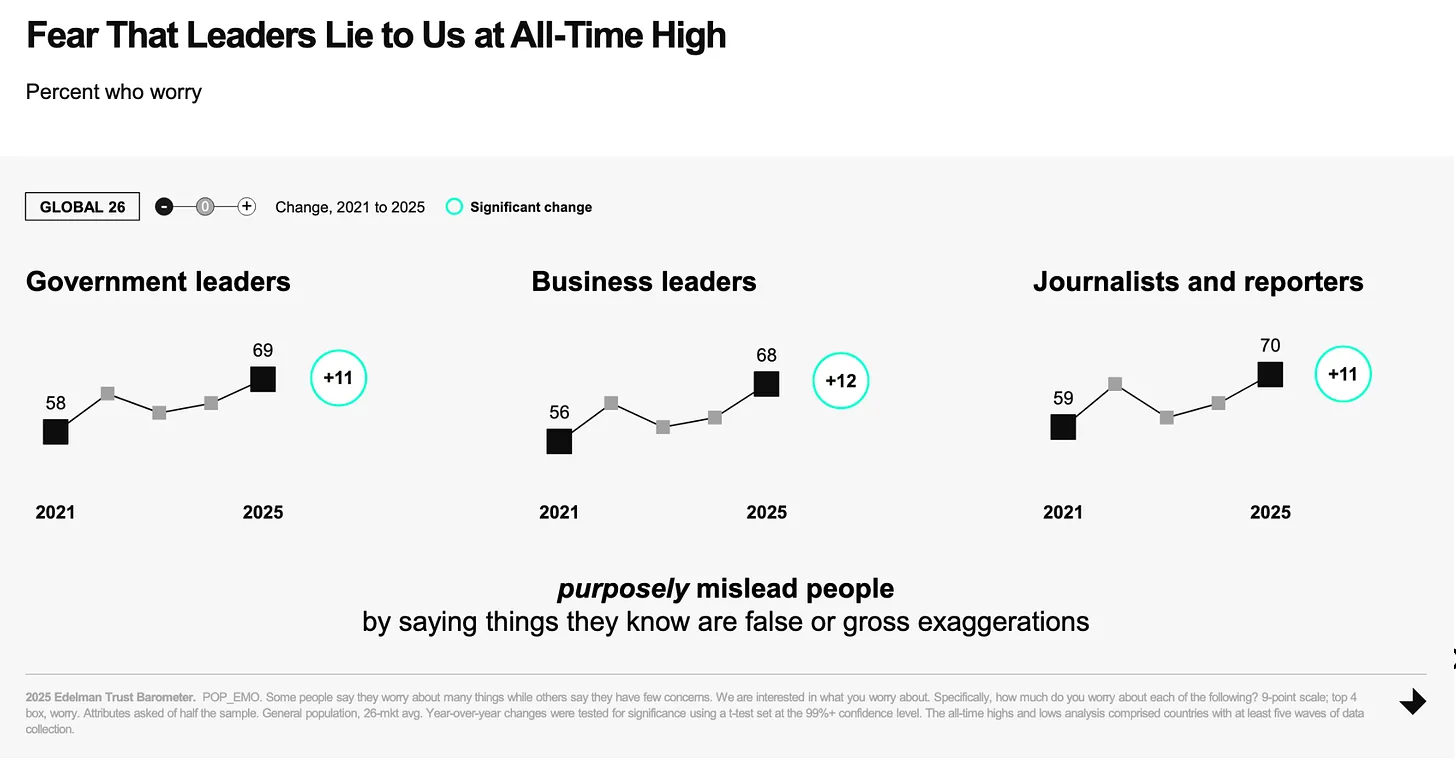 ### Update on the [Pareto project](https://pareto.space/en)  “Half the victory”, says Sun Tsu, ‘lies in the impregnable defense’. Free media now have the opportunity to build their own impregnable bastion and the [Pareto Project](https://pareto.space/read) invites them to do just that: [become uncensorable, be able to scale infinitely and not depend on third parties for all processes of journalistic work](https://pareto.space/a/naddr1qqxnzdenxuerxdpkxycngvpcqgsvlutjpemmkp50p6aa8zwu65yz9hg6erf2czc0tuyqpt57zhr79vsrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hs33ee7d). It's all possible now. Everyone has to realize that: With other platforms, you build your house on someone else's property. With Nostr/Pareto, there is nothing and no one between author and reader, both in terms of communication and payment (via Bitcoin/Lightning). **A brief update on the project, January was very busy.** * We have about 35 journalists, publications, substackers, bloggers, memers onboarded who publish texts via the Pareto client, and the number is growing all the time. * The first Telepolis authors, such as Mathias Bröckers and Alexander Unzicker, will soon be able to re-publish their deleted texts with us in a censorship-proof manner, and we are helping with the migration of content. * We recently successfully tested the newsletter function! We will soon be able to offer all authors and readers the functions of Substack, Steady, Ghost etc. without having to entrust their readers' sensitive data to a platform or expose them to platform tracking. * We are delighted to have more high-caliber additions to our development team, which now comprises around ten wonderful people, almost all of whom come from this group of readers. * Our [open source code is now also public.](https://github.com/twenty-eighty/pareto-client) * We have opened a [crowdfunding on Geyser!](https://geyser.fund/project/pareto) - Our editor will soon be available to everyone free of charge (atm you have to drop us your npub: <team@pareto.space>) ### What's next? This opens up a new window of unimagined possibilities: On a strong basis such as that offered by decentralized technology, many critical authors can now publish securely or new publications can be created - worldwide and uncensorable. What kind of publications would you like to see? Where do you see gaps (also in the critical spectrum) that need to be filled, both in terms of formats and topics? What does the journalism of the future look like to you? Feel free to write to me: **<milosz@pareto.space>** ## One last thing Our funds are coming to an end. If you would like to support us: We have started a [crowdfunding on Geyser](https://geyser.fund/project/pareto), where you can help us with Bitcoin/Lightning donations.   For traditional donations, you can find our bank account on our **[landingpage.](https://pareto.space/en)** *** ***Join the marketplace of ideas!** We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the [Pareto Project](https://pareto.space/en)? Zap me, if you want to contribute (all Zaps go to the project).* *Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to **<team@pareto.space>*** **Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)**
@ e373ca41:b82abcc5
2025-02-13 22:27:58*This article has been written with the* ***[Pareto client](https://pareto.space/read).*** *(read it there for the full experience). It was first published in German by Milosz Matuschek on* ***["Freischwebende Intelligenz".](https://www.freischwebende-intelligenz.org/p/unterwanderter-journalismus-der-mediale)*** *** It is unmistakable. The hydra of the Deep State is losing a few heads - and this time it's the turn of the media heads. Anyone can look at [USASpending](https://www.usaspending.gov/) to see how much taxpayers' money has gone to whom in the USA. ### When the state pays its advocates The mainstream media were also among the beneficiaries: Politico (100% Axel Springer) received over [USD 7 million](https://www.usaspending.gov/recipient/fa0cefae-7cfb-881d-29c3-1bd39cc6a49e-C/latest); the New York Times received over USD 40 million. Thousands of (probably not always necessary) government subscriptions flowed to large media houses - paid for with taxpayers' money. A form of covert press financing by the state. At what point can or should we speak of state media? ") However, this is only the tip of the iceberg. The CIA front organization USAID ([known for its funding of virus research in Wuhan and other questionable activities](https://pareto.space/a/naddr1qqxnzden8quryveexq6rywp3qgswxu72gyq7ykjdfl9j556887jpzwu3mw3v9ez36quas55whq4te3grqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsz9nhwden5te0wfjkccte9ehx7um5wghxyctwvszsxfjh)) - [pumped USD 472.6 million directly into the media landscape via the “Internews Network”.](https://www.zerohedge.com/political/usaid-funded-massive-global-state-propaganda-news-matrix-nearly-billion-people-reach) FAZ journalist Udo Ulfkotte once called this “bought journalists” in a very clear and media-effective way, which was not good for his health. There is ample evidence of the CIA-USAID connections, for example [here](https://timesofindia.indiatimes.com/toi-plus/international/how-usaid-worked-alongside-cia-in-vietnam-a-whistleblowers-account/articleshow/118164225.cms), [here](https://foreignpolicy.com/2014/04/03/cuban-twitter-and-other-times-usaid-pretended-to-be-an-intelligence-agency/) and [here.](https://www.jstor.org/stable/4017728) ") But this is now over for the time being: USD 268 million, which was to go to “independent media for the free flow of information” (according to the [Columbia Journalism Review](https://www.cjr.org/the_media_today/usaid-and-the-media-in-a-time-of-monsters.php)) in 2025, has been frozen. The largest media influence machine in the Western world is bleeding a little. One has to admit: part of the media-deepstate swamp is actually being drained dry financially. The fact that the Columbia Journalism Review doesn't even seem to notice that “free international journalism”, which, as it writes, is largely funded by USAID, ceases to be “free journalism” speaks volumes about this “hotbed of journalism”. Matt Taibbi of Racket News rightly finds, “The legacy media system is dead. They just don't know it yet.” *** ADVERTISEMENT: *Looking for the easiest way to buy Bitcoin and store it yourself? The **[Relai app](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. **[Here you can buy Bitcoin](https://relai.app/de/?af_xp=custom\&source_caller=ui\&pid=INFLUENCER\&is_retargeting=true\&af_click_lookback=7d\&shortlink=eo5zpzew\&af_channel=branded_url\&af_inactivity_window=30d\&c=Milosz%20Matuszek)** in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.*  *Need more security? The **[Trezor wallets](https://trezor.io/trezor-safe-5-bitcoin-only?transaction_id=102e192a206d1585e56a2fddef6d83\&offer_id=238\&affiliate_id=35234)** are recommended and easy to use, others are available in the **[store](https://trezor.io/?transaction_id=102bc85bdca2733287749c7f879ebd\&offer_id=133\&affiliate_id=35234)**. Need more advice? Book an **[introductory meeting](https://trezor.io/trezor-expert-session?transaction_id=1020e18dad0aa4b1186289fd22e90f\&offer_id=241\&affiliate_id=35234)** with a wallet expert.* *** Large-scale media manipulation has become visible. The propaganda matrix, if you will. The disastrous thing about it: if the Overton window is infiltrated, so to speak, the entire institution of journalism cannot be trusted. Every day, readers must expect to be pulled through the nose ring of intelligence service narratives and public agendas by mainstream journalists who pretend to be objective (and are often simply clueless and unsuspecting). The panorama of what we are supposed to see and believe, so to speak. How many mainstream journalists today are basically mouthpieces for the services? Every mainstream reader must now ask themselves: Is my favorite journalist at NZZ, Welt, SZ, ZEIT or FAZ perhaps just a CIA-IM? There were no major dissenters among them: EU criticism? Vaccination criticism? Criticism of NATO? Criticism of Biden and America? Criticism of Nord Stream? There were brief moments on television when questions about journalists' ties to lobby organizations were still part of the German satire program. <https://x.com/Spitze_Zunge_/status/1887915509988876786> ### The cards in the media are being reshuffled The watchdog of the powerful has been infiltrated by the powerful. This means that the Fourth Power is not a power at all, but part of the executive branch, a mouthpiece of the government. The claim that the mainstream is quality journalism, the gold standard for trustworthy information, is therefore the real fake news. It is the last, now crumbling dogma of an infiltrated press sect that has formed a cartel and is subjecting citizens to a permanent psy-op with intelligence-controlled taxpayers' money. A troupe of spokespeople at the work of mental synchronization. <https://x.com/TopherField/status/1887962959072149989> ### The fight against independent media But they not only give to one, they also take from the other. While government agencies use taxpayers' money to promote a certain type of journalism, the juice is actively being cut off from the critical part. All it takes is to be classified as a “PEP” (politically exposed person) and the bank account is gone. This is what has just happened to swiss Radio Kontrafunk. The critical Swiss author Stefan Millius was canceled by his publisher. Others have had their monetization via YouTube cut off (Snicklink). Others are harassed by the state media authority (Multipolar, Alexander Wallasch). The next one has a house search. It has been known since the Twitter files that the government and services also intervened massively in social media communication. This is no longer the Cold War. But it is the cold information war. <https://www.youtube.com/watch?v=kmgWAGDFCZI> Is this all so outrageous and new? During the Cold War, the CIA systematically infiltrated media outlets in the US. Thousands of agents were deployed as journalists - and wrote what they were told. This “Operation Mockingbird”, which the Church Committee also investigated, never ended, so to speak. It lives on as Operation Mockingbird 2.0. Intelligence payments to media outlets continue to exist. USAID distributes millions for “pro-democratic” reporting. Government subscriptions keep uncritical media alive. Media control of public opinion is the most important tool of power in a modern “democracy”. The difference to back then? Today, the manipulation is global. However, these revelations come at a time when trust in the media is already at an all-time low. [The fear of being lied to by the powerful is currently the majority opinion at 70%.](https://www.edelman.com/trust/2025/trust-barometer) They are currently in the process of convincing the remaining 30% of their own incompetence. 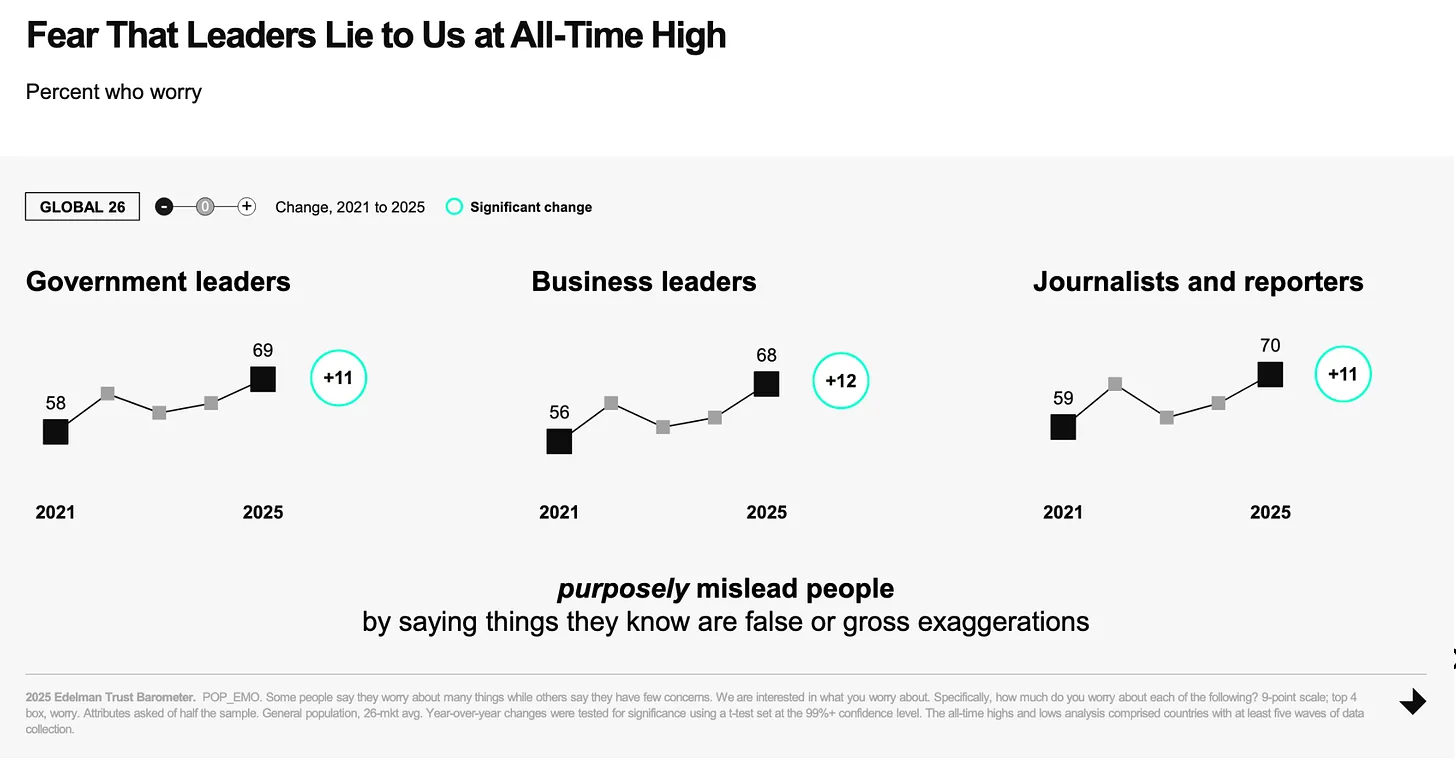 ### Update on the [Pareto project](https://pareto.space/en)  “Half the victory”, says Sun Tsu, ‘lies in the impregnable defense’. Free media now have the opportunity to build their own impregnable bastion and the [Pareto Project](https://pareto.space/read) invites them to do just that: [become uncensorable, be able to scale infinitely and not depend on third parties for all processes of journalistic work](https://pareto.space/a/naddr1qqxnzdenxuerxdpkxycngvpcqgsvlutjpemmkp50p6aa8zwu65yz9hg6erf2czc0tuyqpt57zhr79vsrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hs33ee7d). It's all possible now. Everyone has to realize that: With other platforms, you build your house on someone else's property. With Nostr/Pareto, there is nothing and no one between author and reader, both in terms of communication and payment (via Bitcoin/Lightning). **A brief update on the project, January was very busy.** * We have about 35 journalists, publications, substackers, bloggers, memers onboarded who publish texts via the Pareto client, and the number is growing all the time. * The first Telepolis authors, such as Mathias Bröckers and Alexander Unzicker, will soon be able to re-publish their deleted texts with us in a censorship-proof manner, and we are helping with the migration of content. * We recently successfully tested the newsletter function! We will soon be able to offer all authors and readers the functions of Substack, Steady, Ghost etc. without having to entrust their readers' sensitive data to a platform or expose them to platform tracking. * We are delighted to have more high-caliber additions to our development team, which now comprises around ten wonderful people, almost all of whom come from this group of readers. * Our [open source code is now also public.](https://github.com/twenty-eighty/pareto-client) * We have opened a [crowdfunding on Geyser!](https://geyser.fund/project/pareto) - Our editor will soon be available to everyone free of charge (atm you have to drop us your npub: <team@pareto.space>) ### What's next? This opens up a new window of unimagined possibilities: On a strong basis such as that offered by decentralized technology, many critical authors can now publish securely or new publications can be created - worldwide and uncensorable. What kind of publications would you like to see? Where do you see gaps (also in the critical spectrum) that need to be filled, both in terms of formats and topics? What does the journalism of the future look like to you? Feel free to write to me: **<milosz@pareto.space>** ## One last thing Our funds are coming to an end. If you would like to support us: We have started a [crowdfunding on Geyser](https://geyser.fund/project/pareto), where you can help us with Bitcoin/Lightning donations.   For traditional donations, you can find our bank account on our **[landingpage.](https://pareto.space/en)** *** ***Join the marketplace of ideas!** We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the [Pareto Project](https://pareto.space/en)? Zap me, if you want to contribute (all Zaps go to the project).* *Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to **<team@pareto.space>*** **Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)** @ dbb19ae0:c3f22d5a
2025-02-13 20:42:08Installation: ``` bash python3 -venv nostr-sdk source nostr-sdk/bin/activate pip install nostr_sdk requests ``` Python program: ``` python # Usage example: python ns_read_metadata.py nostr:npub1mwce4c8qa2zn9zw9f372syrc9dsnqmyy3jkcmpqkzaze0slj94dqu6nmwy # Compatible with version 0.39 # ns_read_metadata.py # version 3 import asyncio, argparse, json from nostr_sdk import Metadata, Client, NostrSigner, Keys, Filter, PublicKey, Kind from datetime import timedelta async def main(npub): client = Client() await client.add_relay("wss://relay.damus.io") await client.connect() pk = PublicKey.parse(npub) print(f"\nGetting profile metadata for {npub}:") metadata = await client.fetch_metadata(pk, timedelta(seconds=15)) print(metadata) if __name__ == '__main__': parser = argparse.ArgumentParser(description='Fetch all metadata for a given npub') parser.add_argument('npub', type=str, help='The npub of the user') args = parser.parse_args() asyncio.run(main(args.npub)) ```
@ dbb19ae0:c3f22d5a
2025-02-13 20:42:08Installation: ``` bash python3 -venv nostr-sdk source nostr-sdk/bin/activate pip install nostr_sdk requests ``` Python program: ``` python # Usage example: python ns_read_metadata.py nostr:npub1mwce4c8qa2zn9zw9f372syrc9dsnqmyy3jkcmpqkzaze0slj94dqu6nmwy # Compatible with version 0.39 # ns_read_metadata.py # version 3 import asyncio, argparse, json from nostr_sdk import Metadata, Client, NostrSigner, Keys, Filter, PublicKey, Kind from datetime import timedelta async def main(npub): client = Client() await client.add_relay("wss://relay.damus.io") await client.connect() pk = PublicKey.parse(npub) print(f"\nGetting profile metadata for {npub}:") metadata = await client.fetch_metadata(pk, timedelta(seconds=15)) print(metadata) if __name__ == '__main__': parser = argparse.ArgumentParser(description='Fetch all metadata for a given npub') parser.add_argument('npub', type=str, help='The npub of the user') args = parser.parse_args() asyncio.run(main(args.npub)) ``` @ dd664d5e:5633d319
2025-02-12 07:05:51I think this note from Chip (nostr:npub1qdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havq03fqm7) is one of those things that people with business management experience take a lot more seriously than most developers and influencers do. I am painfully aware of the cost of systems administration, financial transaction management and recordkeeping, recruiting and personnel management, legal and compliance, requirements management, technical support, renting and managing physical spaces and infrastructure, negotiating with suppliers, customer service, etc. etc. There's this idea, on Nostr, that sort of trickled in along with Bitcoin Twitter, that we would all just be isolated subsistance farmers and one-man-show podcasters with a gigantic server rack in the basement. But some of us are running real companies -- on and off Nostr, for-profit and non-profit -- and it often requires a lot of human labor. The things we build aren't meant to be used by one person and his girlfriend and his dog. Yes, he can also run all these things, himself, but he no longer has to. Our existence gives him the choice: run these things or pay us to run them and spend your time doing something else, that you do better than we do. These things are meant to be used by hundreds... thousands... eventually millions of people. The workflows, processes, infrastructure, and personnel need to be able to scale up-and-down, scale in-and-out, work smoothly with 5 people or 50 people. These are the sort of Nostr systems that wouldn't collapse when encountering a sudden influx or mass-escape. But these systems are much more complex and they take time to build and staff to run them. (And, no, AI can't replace them all. AI means that they now also have to integrate a bunch of AI into the system and maintain that, too.) GitCitadel (nostr:npub1s3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqd975wz) is very automation-forward, but we still have to front the incredibly high cost of designing and building the automation, train people to interact with it (there are now over 20 people integrated into the workflow!), adjust it based upon their feedback, and we have to support the automation, once it's running. This sort of streamlined machine is what people pay companies for, not code. That is why there's little business cost to open source. Open-source is great, but...  nostr:nevent1qqsgqh2dedhagyd9k8yfk2lagswjl7y627k9fpnq4l436ccmlys0s3qprdmhxue69uhhg6r9vehhyetnwshxummnw3erztnrdakj7q3qqdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havqxpqqqqqqzdhnyjm
@ dd664d5e:5633d319
2025-02-12 07:05:51I think this note from Chip (nostr:npub1qdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havq03fqm7) is one of those things that people with business management experience take a lot more seriously than most developers and influencers do. I am painfully aware of the cost of systems administration, financial transaction management and recordkeeping, recruiting and personnel management, legal and compliance, requirements management, technical support, renting and managing physical spaces and infrastructure, negotiating with suppliers, customer service, etc. etc. There's this idea, on Nostr, that sort of trickled in along with Bitcoin Twitter, that we would all just be isolated subsistance farmers and one-man-show podcasters with a gigantic server rack in the basement. But some of us are running real companies -- on and off Nostr, for-profit and non-profit -- and it often requires a lot of human labor. The things we build aren't meant to be used by one person and his girlfriend and his dog. Yes, he can also run all these things, himself, but he no longer has to. Our existence gives him the choice: run these things or pay us to run them and spend your time doing something else, that you do better than we do. These things are meant to be used by hundreds... thousands... eventually millions of people. The workflows, processes, infrastructure, and personnel need to be able to scale up-and-down, scale in-and-out, work smoothly with 5 people or 50 people. These are the sort of Nostr systems that wouldn't collapse when encountering a sudden influx or mass-escape. But these systems are much more complex and they take time to build and staff to run them. (And, no, AI can't replace them all. AI means that they now also have to integrate a bunch of AI into the system and maintain that, too.) GitCitadel (nostr:npub1s3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqd975wz) is very automation-forward, but we still have to front the incredibly high cost of designing and building the automation, train people to interact with it (there are now over 20 people integrated into the workflow!), adjust it based upon their feedback, and we have to support the automation, once it's running. This sort of streamlined machine is what people pay companies for, not code. That is why there's little business cost to open source. Open-source is great, but...  nostr:nevent1qqsgqh2dedhagyd9k8yfk2lagswjl7y627k9fpnq4l436ccmlys0s3qprdmhxue69uhhg6r9vehhyetnwshxummnw3erztnrdakj7q3qqdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havqxpqqqqqqzdhnyjm @ 3ad01248:962d8a07
2025-02-13 20:03:40I feel like this is go to be a common phrase over the next four years. While I generally like most of the policies that he is in favor of, I for the life of me can't understand his position on Gaza. It sounds like nothing like the Trump for the campaign trail whatsoever. When he ran for president last year he ran on a platform of not starting any new wars. Having a US solider set foot in Gaza is a recipe for disaster and chaos. Sending in the military is not "America First". Gaza has no national security implication for the United States so obviously there is a different reason why President Trump is proposing this idea. We have to look at who funded his campaign to understand his motives by wanting to clear out Gaza and rebuild it like it some real estate deal. ## Miriam Adelson [Miriam Adelson the wife of late casino magnate Sheldon Adelson](https://www.timesofisrael.com/miriam-adelson-gives-100-million-to-trump-campaign-making-good-on-reported-pledge/) gave Trump $100 million to help get Trump elected. Mrs. Adelson is a pro-Israel and supports a variety of Jewish causes. $100 million buys you a lot of political favors if you ask me. Mrs. Adelson and her husband were the power behind the scene of the first Trump administration to get them to move the US embassy to Jerusalem. She also own the largest newspaper in Israel which means she has the ability to impact public opinion inside the country. As you can see this is person with a tremendous amount money and social capital to spend and she is undoubtedly using it to get Trump to purge Gaza of the native Palestinians. Who else is in Trump's ear that influence him to come up with crazy idea? ### Jared Kushner We all know that Trump values family and loyalty above all else so it is no surprise that Trump would listen to someone in his family for guidance on what to do in Gaza. Jared Kushner is that guy for Trump. As the son-in-law of is favorite daughter you can bet that he is going to listen to what he has to say. Funny you listen to Trump and I swear that you hear Jared come out of his mouth. Back in March 2024 Kushner suggest the very idea that Trump is talking about right now! Almost verbatim to be honest. Here is a link to a talk where Kushner laid out what he thought should happen to Gaza and the Palestinians. https://www.youtube.com/watch?v=nneWrllngAU When you listen to it, you see that Trump basically took this idea from Kushner and made it his own. Who is exactly is running the show in the White House? Trump seems to be doing the bidding of everyone else except the American people. Who else is Trump listening to on the Gaza issue? #### Bibi Netanyahu/Israeli Far-Right Last but not least is the persons behind all the death and mayhem in Gaza. Trump absolutely sides with the Israeli narrative spun by Bibi Netanyahu and the Israeli far right characters such as Itamar Ben-Gvir and Bezalel Smotrich. This trio have a distinct hatred of Palestinians and do not want to see the creation of a Palestinian state. They want to see occupied West Bank annexed by Israel and all of the Palestinians there to leave or be subjugated to Israeli rule. Just take a look at the worldview of these people and they have power within the halls of the Israeli government. https://www.jpost.com/Israel-News/Politics-And-Diplomacy/Bayit-Yehudi-MK-causes-uproar-by-saying-God-commanded-Jews-not-to-sell-homes-to-Arabs-409241 https://hashiloach.org.il/israels-decisive-plan/ https://www.reuters.com/article/idUSKBN0MC1I7/ When you have this world view how is peace even possible? It's not because they don't want peace and quite frankly I don't know if its possible at this point. Israelis and Palestinians have diametrically opposing views of what the land should be. Israeli believe that the land should be exclusively governed by Jewish people whereas the Palestinian view from what I understand just want to return to the lands they were kicked out from and deal with governance later. There are elements on both side that want this conflict to go on forever because it gives the outsized power, namely Hamas on the Palestinian side and the Israeli Far Right on the Jewish side. I would guess that a majority of people in the middle would have no problem living side by side with each other as long as rights and freedoms were respected. A one state solution looks like the most reasonable solution to me but the odds of that happening are slim to none right now. President Trump has the power to change the middle east for the better if he had the backbone do to what is right but it looks like he is going to listen to people the want war, genocide and ethnic cleansing.
@ 3ad01248:962d8a07
2025-02-13 20:03:40I feel like this is go to be a common phrase over the next four years. While I generally like most of the policies that he is in favor of, I for the life of me can't understand his position on Gaza. It sounds like nothing like the Trump for the campaign trail whatsoever. When he ran for president last year he ran on a platform of not starting any new wars. Having a US solider set foot in Gaza is a recipe for disaster and chaos. Sending in the military is not "America First". Gaza has no national security implication for the United States so obviously there is a different reason why President Trump is proposing this idea. We have to look at who funded his campaign to understand his motives by wanting to clear out Gaza and rebuild it like it some real estate deal. ## Miriam Adelson [Miriam Adelson the wife of late casino magnate Sheldon Adelson](https://www.timesofisrael.com/miriam-adelson-gives-100-million-to-trump-campaign-making-good-on-reported-pledge/) gave Trump $100 million to help get Trump elected. Mrs. Adelson is a pro-Israel and supports a variety of Jewish causes. $100 million buys you a lot of political favors if you ask me. Mrs. Adelson and her husband were the power behind the scene of the first Trump administration to get them to move the US embassy to Jerusalem. She also own the largest newspaper in Israel which means she has the ability to impact public opinion inside the country. As you can see this is person with a tremendous amount money and social capital to spend and she is undoubtedly using it to get Trump to purge Gaza of the native Palestinians. Who else is in Trump's ear that influence him to come up with crazy idea? ### Jared Kushner We all know that Trump values family and loyalty above all else so it is no surprise that Trump would listen to someone in his family for guidance on what to do in Gaza. Jared Kushner is that guy for Trump. As the son-in-law of is favorite daughter you can bet that he is going to listen to what he has to say. Funny you listen to Trump and I swear that you hear Jared come out of his mouth. Back in March 2024 Kushner suggest the very idea that Trump is talking about right now! Almost verbatim to be honest. Here is a link to a talk where Kushner laid out what he thought should happen to Gaza and the Palestinians. https://www.youtube.com/watch?v=nneWrllngAU When you listen to it, you see that Trump basically took this idea from Kushner and made it his own. Who is exactly is running the show in the White House? Trump seems to be doing the bidding of everyone else except the American people. Who else is Trump listening to on the Gaza issue? #### Bibi Netanyahu/Israeli Far-Right Last but not least is the persons behind all the death and mayhem in Gaza. Trump absolutely sides with the Israeli narrative spun by Bibi Netanyahu and the Israeli far right characters such as Itamar Ben-Gvir and Bezalel Smotrich. This trio have a distinct hatred of Palestinians and do not want to see the creation of a Palestinian state. They want to see occupied West Bank annexed by Israel and all of the Palestinians there to leave or be subjugated to Israeli rule. Just take a look at the worldview of these people and they have power within the halls of the Israeli government. https://www.jpost.com/Israel-News/Politics-And-Diplomacy/Bayit-Yehudi-MK-causes-uproar-by-saying-God-commanded-Jews-not-to-sell-homes-to-Arabs-409241 https://hashiloach.org.il/israels-decisive-plan/ https://www.reuters.com/article/idUSKBN0MC1I7/ When you have this world view how is peace even possible? It's not because they don't want peace and quite frankly I don't know if its possible at this point. Israelis and Palestinians have diametrically opposing views of what the land should be. Israeli believe that the land should be exclusively governed by Jewish people whereas the Palestinian view from what I understand just want to return to the lands they were kicked out from and deal with governance later. There are elements on both side that want this conflict to go on forever because it gives the outsized power, namely Hamas on the Palestinian side and the Israeli Far Right on the Jewish side. I would guess that a majority of people in the middle would have no problem living side by side with each other as long as rights and freedoms were respected. A one state solution looks like the most reasonable solution to me but the odds of that happening are slim to none right now. President Trump has the power to change the middle east for the better if he had the backbone do to what is right but it looks like he is going to listen to people the want war, genocide and ethnic cleansing. @ c69b71dc:426ba763
2025-02-11 14:07:34# The Power of Words... ## ...Shaping a Compassionate Future This morning I woke up with this thought: **> If we were more mindful of our choice of words, we would immediately need to change the following: Schools would no longer have classes and classifications, but only Communities!** This would make a huge difference in terms of togetherness, well-being, and caring for one another. 🙌🏼 ### Language shapes reality Words influence how we see the world and ourselves. When we replace terms like "classes" or "grades" with "community" and "development," it changes our entire way of thinking about education and coexistence. For example, in companies, we often talk about "teams" instead of "departments." This unconsciously fosters unity, cooperation, and a sense of belonging on equal terms. ### Community instead of competition In school, work, and everyday life, we often evaluate, compare, and classify. But what if we focused on cooperation and synergies instead of competition? In some schools, there are no grades anymore, just individual feedback – this takes away the performance pressure and strengthens intrinsic motivation. ### Appreciation instead of categorization Putting people in "boxes" – whether through grading systems, social classes, or job titles – often creates separation rather than connection. Instead of labeling people as "successful" or "failed," we could ask: "What are their strengths? How can we support each other?" Mindful language in everyday life We could also reflect on our word choices in daily life: Instead of "problem" → "challenge" Instead of "failure" → "learning opportunity" Instead of "mistake" → "experience" ### School as a mirror of society How we learn to interact with each other in school shapes our behavior in society. When children grow up in communities instead of class systems, they learn that cooperation and empathy are more important than competition. There are so-called democratic schools where there are no grade levels – children learn from each other across ages. Students support each other by sharing knowledge and helping each other. Teachers are seen as coaches, not as "all-knowing" authority figures. They too are human and can learn from the children. Many teachers want to give children something that will help them in life. However, the rigid old school system dictates what must be taught and when, often disregarding the individual interests of the children. This stifles passions – in both the children and the teachers. Instead, teachers could act as inspiring sparks, igniting curiosity and enthusiasm for learning. ----------- > **A history teacher once said to me on the phone, when discussing my son who didn’t want to read printed Wikipedia sheets: "If there is no spark in the child, the teacher can’t ignite anything." ** This sentence frustrated me, because it shows that this teacher had long since lost his own spark! **Children always have a spark. Always!** ----------- ### A day without evaluations What if we consciously refrained from evaluating others for one day – whether through grades, criticism, or labels? Instead of saying to a friend, "You made a mistake," we could say, "That was an interesting experience – what did you learn from it?" Instead of saying, "That wasn’t good," we could ask, "How could it be done differently or better?" Instead of grading children in school, we could tell them what they did well and where they can still grow. Instead of getting upset about a difficult customer, we could feel empathy for their situation. ### Mindful language as the key to change **If we are more mindful with our language – also with how we speak to ourselves – we can shape a society where people meet each other with compassion. ** `Words are vibrations that shape reality. Chosen consciously, they can create a world based on connection, growth, and love. It is up to us to start this change within ourselves – and carry it into the world.` Thank you for reading 🕊️ 
@ c69b71dc:426ba763
2025-02-11 14:07:34# The Power of Words... ## ...Shaping a Compassionate Future This morning I woke up with this thought: **> If we were more mindful of our choice of words, we would immediately need to change the following: Schools would no longer have classes and classifications, but only Communities!** This would make a huge difference in terms of togetherness, well-being, and caring for one another. 🙌🏼 ### Language shapes reality Words influence how we see the world and ourselves. When we replace terms like "classes" or "grades" with "community" and "development," it changes our entire way of thinking about education and coexistence. For example, in companies, we often talk about "teams" instead of "departments." This unconsciously fosters unity, cooperation, and a sense of belonging on equal terms. ### Community instead of competition In school, work, and everyday life, we often evaluate, compare, and classify. But what if we focused on cooperation and synergies instead of competition? In some schools, there are no grades anymore, just individual feedback – this takes away the performance pressure and strengthens intrinsic motivation. ### Appreciation instead of categorization Putting people in "boxes" – whether through grading systems, social classes, or job titles – often creates separation rather than connection. Instead of labeling people as "successful" or "failed," we could ask: "What are their strengths? How can we support each other?" Mindful language in everyday life We could also reflect on our word choices in daily life: Instead of "problem" → "challenge" Instead of "failure" → "learning opportunity" Instead of "mistake" → "experience" ### School as a mirror of society How we learn to interact with each other in school shapes our behavior in society. When children grow up in communities instead of class systems, they learn that cooperation and empathy are more important than competition. There are so-called democratic schools where there are no grade levels – children learn from each other across ages. Students support each other by sharing knowledge and helping each other. Teachers are seen as coaches, not as "all-knowing" authority figures. They too are human and can learn from the children. Many teachers want to give children something that will help them in life. However, the rigid old school system dictates what must be taught and when, often disregarding the individual interests of the children. This stifles passions – in both the children and the teachers. Instead, teachers could act as inspiring sparks, igniting curiosity and enthusiasm for learning. ----------- > **A history teacher once said to me on the phone, when discussing my son who didn’t want to read printed Wikipedia sheets: "If there is no spark in the child, the teacher can’t ignite anything." ** This sentence frustrated me, because it shows that this teacher had long since lost his own spark! **Children always have a spark. Always!** ----------- ### A day without evaluations What if we consciously refrained from evaluating others for one day – whether through grades, criticism, or labels? Instead of saying to a friend, "You made a mistake," we could say, "That was an interesting experience – what did you learn from it?" Instead of saying, "That wasn’t good," we could ask, "How could it be done differently or better?" Instead of grading children in school, we could tell them what they did well and where they can still grow. Instead of getting upset about a difficult customer, we could feel empathy for their situation. ### Mindful language as the key to change **If we are more mindful with our language – also with how we speak to ourselves – we can shape a society where people meet each other with compassion. ** `Words are vibrations that shape reality. Chosen consciously, they can create a world based on connection, growth, and love. It is up to us to start this change within ourselves – and carry it into the world.` Thank you for reading 🕊️  @ 21ffd29c:518a8ff5
2025-02-13 20:03:17**Introduction:** Self sovereignty is a pivotal concept in understanding personal autonomy across various ideologies, including, libertarianism, socialism and individualism. This article explores how the statement "I own myself" by the Ole Voyager in the 1600's encapsulates this principle, emphasizing empowerment and self-management. **Article:** - **What is Self Sovereignty?** - **Definition:** It refers to the ability of an individual or group to govern themselves without external imposition. - **Core Principles:** - Autonomy: The right to manage one's own affairs independently. - Equality: Recognition of equal rights and responsibilities among individuals. - **Historical Context:** Rooted in ideas from liberalism, socialism, and feminism, advocating for personal freedom and equality. - **The Significance of 'I Own Myself'** - **Statement Explanation:** The Ole Voyager's quote highlights personal ownership over one's life, values, and destiny. - **Contrast with Traditional Views:** Shifts from societal control to individual responsibility, advocating for personal agency. - **Implications:** Encourages owning health, relationships, knowledge, and cultural identity, promoting a holistic view of self-worth. **Conclusion:** Understanding self sovereignty through the Ole Voyager's statement is crucial. It empowers individuals by asserting their right to manage their lives autonomously. This concept not only enhances personal freedom but also challenges societal structures, fostering inclusive governance that respects individual rights and equality. Not everyone has the capacity to be a sovereign and self govern themselves. Some are quite content to be told what to do and how to do it. Others are very happy to be on the dole and get free things in exchange for trinkets. This empowerment can lead to more equitable societies where individuals thrive within their own means, emphasizing empowerment and collective responsibility.
@ 21ffd29c:518a8ff5
2025-02-13 20:03:17**Introduction:** Self sovereignty is a pivotal concept in understanding personal autonomy across various ideologies, including, libertarianism, socialism and individualism. This article explores how the statement "I own myself" by the Ole Voyager in the 1600's encapsulates this principle, emphasizing empowerment and self-management. **Article:** - **What is Self Sovereignty?** - **Definition:** It refers to the ability of an individual or group to govern themselves without external imposition. - **Core Principles:** - Autonomy: The right to manage one's own affairs independently. - Equality: Recognition of equal rights and responsibilities among individuals. - **Historical Context:** Rooted in ideas from liberalism, socialism, and feminism, advocating for personal freedom and equality. - **The Significance of 'I Own Myself'** - **Statement Explanation:** The Ole Voyager's quote highlights personal ownership over one's life, values, and destiny. - **Contrast with Traditional Views:** Shifts from societal control to individual responsibility, advocating for personal agency. - **Implications:** Encourages owning health, relationships, knowledge, and cultural identity, promoting a holistic view of self-worth. **Conclusion:** Understanding self sovereignty through the Ole Voyager's statement is crucial. It empowers individuals by asserting their right to manage their lives autonomously. This concept not only enhances personal freedom but also challenges societal structures, fostering inclusive governance that respects individual rights and equality. Not everyone has the capacity to be a sovereign and self govern themselves. Some are quite content to be told what to do and how to do it. Others are very happy to be on the dole and get free things in exchange for trinkets. This empowerment can lead to more equitable societies where individuals thrive within their own means, emphasizing empowerment and collective responsibility. @ 30b99916:3cc6e3fe
2025-02-13 18:56:37## Upgrade Details Download current release and manifest files ```shell Navigate to https://github.com/getAlby/hub/releases/tag/v1.13.0/ Download albyhub-Server-Linux-x86_64.tar.bz2 manifest.txt manifext.txt.asc Copy the downloaded files to $HOME mv $HOME/Downloads/albyhub-Server-Linux-x86_64.tar.bz2 $HOME mv $HOME/Downloads/manifest.txt $HOME mv $HOME/Downloads/manifest.txt.asc $HOME ``` Verify manifest signature & Checksum ```sh Only need to import once curl https://raw.githubusercontent.com/getalby/hub/master/scripts/keys/rolznz.asc | gpg --import gpg --verify manifest.txt.asc manifest.txt gpg: Signature made Tue 07 Jan 2025 08:56:42 PM PST gpg: using RSA key 5D92185938E6DBF893DCCC5BA5EABD8835092B08 gpg: Good signature from "Roland Bewick <roland.bewick@gmail.com>" [unknown] gpg: WARNING: This key is not certified with a trusted signature! gpg: There is no indication that the signature belongs to the owner. Primary key fingerprint: 5D92 1859 38E6 DBF8 93DC CC5B A5EA BD88 3509 2B08 shasum -a 256 server-linux-x86_64.tar.bz2 a75c03d241921611dfc428c413c4a2c2cef35bc6d1974839b688ef462604058d server-linux-x86_64.tar.bz2 The above checksum should be referenced in the manifest.txt file cat manifest.txt ``` Stop AlbyHub & Backup existing data directory & Binaries ```shell systemctl stop albyhub cp -r $HOME/.local/share/albyhub /media/veracrypt1/albyhub cp $HOME/bin/albyhub $HOME/bin/albyhub172 cp -r $HOME/lib $HOME/lib172 ``` Extract new release Binaries & Start AlbyHub ```sh tar -xvjf albyhub-Server-Linux-x86_64.tar.bz2 ./ ./lib/ ./lib/libglalby_bindings.so ./lib/libldk_node.so ./lib/libbreez_sdk_bindings.so ./bin/ ./bin/albyhub systemctl start albyhub ``` Navigate to http://localhost:9090
@ 30b99916:3cc6e3fe
2025-02-13 18:56:37## Upgrade Details Download current release and manifest files ```shell Navigate to https://github.com/getAlby/hub/releases/tag/v1.13.0/ Download albyhub-Server-Linux-x86_64.tar.bz2 manifest.txt manifext.txt.asc Copy the downloaded files to $HOME mv $HOME/Downloads/albyhub-Server-Linux-x86_64.tar.bz2 $HOME mv $HOME/Downloads/manifest.txt $HOME mv $HOME/Downloads/manifest.txt.asc $HOME ``` Verify manifest signature & Checksum ```sh Only need to import once curl https://raw.githubusercontent.com/getalby/hub/master/scripts/keys/rolznz.asc | gpg --import gpg --verify manifest.txt.asc manifest.txt gpg: Signature made Tue 07 Jan 2025 08:56:42 PM PST gpg: using RSA key 5D92185938E6DBF893DCCC5BA5EABD8835092B08 gpg: Good signature from "Roland Bewick <roland.bewick@gmail.com>" [unknown] gpg: WARNING: This key is not certified with a trusted signature! gpg: There is no indication that the signature belongs to the owner. Primary key fingerprint: 5D92 1859 38E6 DBF8 93DC CC5B A5EA BD88 3509 2B08 shasum -a 256 server-linux-x86_64.tar.bz2 a75c03d241921611dfc428c413c4a2c2cef35bc6d1974839b688ef462604058d server-linux-x86_64.tar.bz2 The above checksum should be referenced in the manifest.txt file cat manifest.txt ``` Stop AlbyHub & Backup existing data directory & Binaries ```shell systemctl stop albyhub cp -r $HOME/.local/share/albyhub /media/veracrypt1/albyhub cp $HOME/bin/albyhub $HOME/bin/albyhub172 cp -r $HOME/lib $HOME/lib172 ``` Extract new release Binaries & Start AlbyHub ```sh tar -xvjf albyhub-Server-Linux-x86_64.tar.bz2 ./ ./lib/ ./lib/libglalby_bindings.so ./lib/libldk_node.so ./lib/libbreez_sdk_bindings.so ./bin/ ./bin/albyhub systemctl start albyhub ``` Navigate to http://localhost:9090 @ dbb19ae0:c3f22d5a
2025-02-13 17:46:41This code below works with nostr_sdk 0.32.2 ``` python import asyncio, argparse, json from nostr_sdk import Metadata, Client, NostrSigner, Keys, Filter, PublicKey, Kind from datetime import timedelta async def main(npub): client = Client() await client.add_relay("wss://relay.damus.io") await client.connect() pk = PublicKey.from_bech32(npub) print(f"Getting profile metadata for {npub}:") f = Filter().kind(Kind(0)).author(pk).limit(1) events = await client.get_events_of([f], timedelta(seconds=15)) if events: event = events[0] metadata_dict = json.loads(event.content()) for key, value in metadata_dict.items(): print(f"{key}: {value}") else: print("Could not retrieve metadata for the given public key.") if __name__ == '__main__': parser = argparse.ArgumentParser(description='Fetch all metadata for a given npub') parser.add_argument('npub', type=str, help='The npub of the user') args = parser.parse_args() asyncio.run(main(args.npub)) ``` but with nostr_sdk 0.39 the program no longer worked and crash with error: ``` AttributeError: type object 'PublicKey' has no attribute 'from_bech32'. Did you mean: 'to_bech32'? ``` why? --- source: - https://github.com/ev3rst/nostr_sdk_examples - https://alashazam.wordpress.com/2024/07/07/python-nostr_sdk-fetching-all-metadata/
@ dbb19ae0:c3f22d5a
2025-02-13 17:46:41This code below works with nostr_sdk 0.32.2 ``` python import asyncio, argparse, json from nostr_sdk import Metadata, Client, NostrSigner, Keys, Filter, PublicKey, Kind from datetime import timedelta async def main(npub): client = Client() await client.add_relay("wss://relay.damus.io") await client.connect() pk = PublicKey.from_bech32(npub) print(f"Getting profile metadata for {npub}:") f = Filter().kind(Kind(0)).author(pk).limit(1) events = await client.get_events_of([f], timedelta(seconds=15)) if events: event = events[0] metadata_dict = json.loads(event.content()) for key, value in metadata_dict.items(): print(f"{key}: {value}") else: print("Could not retrieve metadata for the given public key.") if __name__ == '__main__': parser = argparse.ArgumentParser(description='Fetch all metadata for a given npub') parser.add_argument('npub', type=str, help='The npub of the user') args = parser.parse_args() asyncio.run(main(args.npub)) ``` but with nostr_sdk 0.39 the program no longer worked and crash with error: ``` AttributeError: type object 'PublicKey' has no attribute 'from_bech32'. Did you mean: 'to_bech32'? ``` why? --- source: - https://github.com/ev3rst/nostr_sdk_examples - https://alashazam.wordpress.com/2024/07/07/python-nostr_sdk-fetching-all-metadata/ @ 89ccea93:df4e00b7
2025-02-13 17:34:06**[Original Post](https://expatriotic.me/grapheneos/)** ## Core Philosophy 1. **Privacy ≠ Optional**: Prevents mass data collection by design 2. **Security > Convenience**: Sacrifices "smart" features for exploit resistance 3. **Transparency**: Every line of code [auditable](https://github.com/GrapheneOS) 4. **Device Sanity**: Removes 2M+ lines of Google telemetry code 5. **Proactive Hardening**: Replaces reactive "vulnerability whack-a-mole" with systemic memory safety improvements. 73% of Android CVEs prevented via Scudo++ allocator and Rust integration. 6. **Hardware Paradox**: Uses Google Pixels *because* of their Titan M2 secure enclave (physically separate from main CPU, Verified Boot with user-defined root of trust, Firmware-level MAC randomization (prevents Wi-Fi tracking)). 7. **Support Superiority**: GrapheneOS support for Pixel phones is 2 years longer Google's. > *"We're eliminating entire vulnerability classes - not just patching holes."* ## **History** * Born in **2014** as **CopperheadOS** * **2016**: First Pixel support (Google's hardware + de-Googled OS) * Rebranded in **2019** after a developer split. Focuses exclusively on Pixel phones. * **2021**: **Scudo++** with quarantines (NSA-grade exploit mitigation) * **2023**: Full Rust integration (prevents buffer overflows in core OS) * **2023**: Controversial lead dev, Daniel Micay, stepped down but remains director * **2024**: Quantum-resistant encryption prototypes > *"Our Auditor app detects hardware tampering better than Apple's T2 chip."* ## **Installation** * **Minimum**: Pixel 4a * **Recommended**: Pixel 7a (5-year update guarantee) * **Backup data first**: unlocking bootloader wipes device ### **Beginners: Web Installer** 1. Enable OEM Unlock: `Settings → About → Tap Build Number 7x → Developer Options → OEM Unlocking` 2. Visit [grapheneos.org/install](https://grapheneos.org/install) 3. Connect phone → Follow prompts (20 minutes) ### **Advanced: CLI install** * Full CLI guide: [grapheneos.org/install/cli](https://grapheneos.org/install/cli) (8 minutes) >*"We're proving iPhones aren't the only secure option - just better marketed."* ### **Post-Install Checklist** [ ] Deny all "convenience" permissions [ ] Enable Sensors Off toggle [ ] Install Auditor app [ ] Sensors Killswitch: `Quick Settings → Toggle Off` [ ] Network Restrictions: ```markdown Settings → Network & Internet → Firewall - Enable per-connection MAC randomization - Block local network discovery ``` [ ] Auditor Validation: Daily automated checks against Google's hardware certs ## Setting up ### **Priority Sources** 1. **Accrescent** (Pre-installed) - Molly (Signal fork) - Aves Gallery (EXIF stripping) - AppVerifier (APK validation) 2. **Obtainium** ([GitHub](https://github.com/ImranR98/Obtainium)) ```markdown 1. Search "[App] GitHub releases" 2. Copy releases page URL 3. Paste into Obtainium → Auto-updates enabled ``` - *Example*: NewPipe → `https://github.com/TeamNewPipe/NewPipe/releases` 3. **Google Play** (Last Resort) - Use separate profile - Burner account: Fake name + **NO phone number** ## FOSS Apps * Accrescent - Privacy-focused app store * Aegis - 2FA authenticator * Amethyst - Nostr decentralized social client * AndBible - Offline Bible study * Antennapod - Podcast manager * AppVerifier - APK signature validation * Ashigaru - Bitcoin wallet with Ricochet * Aves Gallery - Gallery with EXIF stripping * Brave - Anti-fingerprinting browser * Easy Noise - Offline white noise generator * Easy Note - Minimalist notes * Envoy - Bitcoin wallet * IronFox - Hardened Firefox fork * KeePassDX - Offline password manager * Léon - URL tracking stripper * LocalSend - AirDrop alternative * Material Files - File manager * Molly - Signal fork with local encyption * Monero.com - Official Monero wallet * NetGuard - No-root firewall * NewPipe - YouTube client with SponsorBlock * Nextcloud - Self-hosted cloud suite * OpenKeychain - PGP encryption * Organic Maps - Offline navigation * Orbot - Tor proxy * Proton Drive - E2E encrypted storage * Proton Mail - Zero-access email * RedReader - Privacy-first Reddit client * Simple Calendar Pro - Telemetry-free calendar * Telegram FOSS - Decentralized messaging * Tor Browser - Onion-routed browsing * Twidere - Twitter/Fediverse client * Tuta - Encrypted email * Tuta Calendar - Encrypted calendar * Vanadium - Hardened Chromium * Zeus - Bitcoin Lightning node > _"Your phone is a corporate surveillance device that happens to make calls. GrapheneOS removes the spyware OS while keeping the secure hardware."_ ## **Silent.Link eSIM: Anonymous Connectivity** **No Phone Number Required** Visit [Silent.Link](https://silent.link) → Select data plus eSIM plan (with NO phone number). ```I've used this successfully in many countries. It even gives me unfettered and free internet in China. Be sure to pick the telecom company based on what they charge per GB of data. The difference can be 100x!``` ## Support the Project: - **Donate**: [grapheneos.org/donate](https://grapheneos.org/donate) - **Community**: [grapheneos.org/contact](https://grapheneos.org/contact) >*"GrapheneOS isn't about becoming a privacy expert overnight. It's about systematically removing corporate surveillance hooks - one app, one permission, one profile at a time."* ## Moar Halp * **[Side Of Burritos](https://www.youtube.com/playlist?list=PLHvdaysg3bMyYwJAcxbFUY9YqKKC0Dtrd)** * **[Hated One interview with GrapheneOS dev Gabe](https://www.youtube.com/watch?v=WkQ_OCzuLNg)** originally posted at https://stacker.news/items/884965
@ 89ccea93:df4e00b7
2025-02-13 17:34:06**[Original Post](https://expatriotic.me/grapheneos/)** ## Core Philosophy 1. **Privacy ≠ Optional**: Prevents mass data collection by design 2. **Security > Convenience**: Sacrifices "smart" features for exploit resistance 3. **Transparency**: Every line of code [auditable](https://github.com/GrapheneOS) 4. **Device Sanity**: Removes 2M+ lines of Google telemetry code 5. **Proactive Hardening**: Replaces reactive "vulnerability whack-a-mole" with systemic memory safety improvements. 73% of Android CVEs prevented via Scudo++ allocator and Rust integration. 6. **Hardware Paradox**: Uses Google Pixels *because* of their Titan M2 secure enclave (physically separate from main CPU, Verified Boot with user-defined root of trust, Firmware-level MAC randomization (prevents Wi-Fi tracking)). 7. **Support Superiority**: GrapheneOS support for Pixel phones is 2 years longer Google's. > *"We're eliminating entire vulnerability classes - not just patching holes."* ## **History** * Born in **2014** as **CopperheadOS** * **2016**: First Pixel support (Google's hardware + de-Googled OS) * Rebranded in **2019** after a developer split. Focuses exclusively on Pixel phones. * **2021**: **Scudo++** with quarantines (NSA-grade exploit mitigation) * **2023**: Full Rust integration (prevents buffer overflows in core OS) * **2023**: Controversial lead dev, Daniel Micay, stepped down but remains director * **2024**: Quantum-resistant encryption prototypes > *"Our Auditor app detects hardware tampering better than Apple's T2 chip."* ## **Installation** * **Minimum**: Pixel 4a * **Recommended**: Pixel 7a (5-year update guarantee) * **Backup data first**: unlocking bootloader wipes device ### **Beginners: Web Installer** 1. Enable OEM Unlock: `Settings → About → Tap Build Number 7x → Developer Options → OEM Unlocking` 2. Visit [grapheneos.org/install](https://grapheneos.org/install) 3. Connect phone → Follow prompts (20 minutes) ### **Advanced: CLI install** * Full CLI guide: [grapheneos.org/install/cli](https://grapheneos.org/install/cli) (8 minutes) >*"We're proving iPhones aren't the only secure option - just better marketed."* ### **Post-Install Checklist** [ ] Deny all "convenience" permissions [ ] Enable Sensors Off toggle [ ] Install Auditor app [ ] Sensors Killswitch: `Quick Settings → Toggle Off` [ ] Network Restrictions: ```markdown Settings → Network & Internet → Firewall - Enable per-connection MAC randomization - Block local network discovery ``` [ ] Auditor Validation: Daily automated checks against Google's hardware certs ## Setting up ### **Priority Sources** 1. **Accrescent** (Pre-installed) - Molly (Signal fork) - Aves Gallery (EXIF stripping) - AppVerifier (APK validation) 2. **Obtainium** ([GitHub](https://github.com/ImranR98/Obtainium)) ```markdown 1. Search "[App] GitHub releases" 2. Copy releases page URL 3. Paste into Obtainium → Auto-updates enabled ``` - *Example*: NewPipe → `https://github.com/TeamNewPipe/NewPipe/releases` 3. **Google Play** (Last Resort) - Use separate profile - Burner account: Fake name + **NO phone number** ## FOSS Apps * Accrescent - Privacy-focused app store * Aegis - 2FA authenticator * Amethyst - Nostr decentralized social client * AndBible - Offline Bible study * Antennapod - Podcast manager * AppVerifier - APK signature validation * Ashigaru - Bitcoin wallet with Ricochet * Aves Gallery - Gallery with EXIF stripping * Brave - Anti-fingerprinting browser * Easy Noise - Offline white noise generator * Easy Note - Minimalist notes * Envoy - Bitcoin wallet * IronFox - Hardened Firefox fork * KeePassDX - Offline password manager * Léon - URL tracking stripper * LocalSend - AirDrop alternative * Material Files - File manager * Molly - Signal fork with local encyption * Monero.com - Official Monero wallet * NetGuard - No-root firewall * NewPipe - YouTube client with SponsorBlock * Nextcloud - Self-hosted cloud suite * OpenKeychain - PGP encryption * Organic Maps - Offline navigation * Orbot - Tor proxy * Proton Drive - E2E encrypted storage * Proton Mail - Zero-access email * RedReader - Privacy-first Reddit client * Simple Calendar Pro - Telemetry-free calendar * Telegram FOSS - Decentralized messaging * Tor Browser - Onion-routed browsing * Twidere - Twitter/Fediverse client * Tuta - Encrypted email * Tuta Calendar - Encrypted calendar * Vanadium - Hardened Chromium * Zeus - Bitcoin Lightning node > _"Your phone is a corporate surveillance device that happens to make calls. GrapheneOS removes the spyware OS while keeping the secure hardware."_ ## **Silent.Link eSIM: Anonymous Connectivity** **No Phone Number Required** Visit [Silent.Link](https://silent.link) → Select data plus eSIM plan (with NO phone number). ```I've used this successfully in many countries. It even gives me unfettered and free internet in China. Be sure to pick the telecom company based on what they charge per GB of data. The difference can be 100x!``` ## Support the Project: - **Donate**: [grapheneos.org/donate](https://grapheneos.org/donate) - **Community**: [grapheneos.org/contact](https://grapheneos.org/contact) >*"GrapheneOS isn't about becoming a privacy expert overnight. It's about systematically removing corporate surveillance hooks - one app, one permission, one profile at a time."* ## Moar Halp * **[Side Of Burritos](https://www.youtube.com/playlist?list=PLHvdaysg3bMyYwJAcxbFUY9YqKKC0Dtrd)** * **[Hated One interview with GrapheneOS dev Gabe](https://www.youtube.com/watch?v=WkQ_OCzuLNg)** originally posted at https://stacker.news/items/884965 @ dbb19ae0:c3f22d5a
2025-02-13 17:32:36pip cache will show how much space is taken from past download ``` bash (nostr) ever3st@Alashazam:~/Documents/dev/python/$ pip cache info Package index page cache location: /home/ever3st/.cache/pip/http Package index page cache size: 2437.7 MB Number of HTTP files: 271 Wheels location: /home/ever3st/.cache/pip/wheels Wheels size: 2.2 MB Number of wheels: 2 ``` About 2GB if space is needed it can be cleared ``` bash (nostr) ever3st@Alashazam:~/Documents/dev/python/$ pip cache purge Files removed: 273 (nostr) ever3st@Alashazam:~/Documents/dev/python/bots/nostr$ pip cache info Package index page cache location: /home/ever3st/.cache/pip/http Package index page cache size: 0 bytes Number of HTTP files: 0 Wheels location: /home/ever3st/.cache/pip/wheels Wheels size: 326 bytes Number of wheels: 0 ```
@ dbb19ae0:c3f22d5a
2025-02-13 17:32:36pip cache will show how much space is taken from past download ``` bash (nostr) ever3st@Alashazam:~/Documents/dev/python/$ pip cache info Package index page cache location: /home/ever3st/.cache/pip/http Package index page cache size: 2437.7 MB Number of HTTP files: 271 Wheels location: /home/ever3st/.cache/pip/wheels Wheels size: 2.2 MB Number of wheels: 2 ``` About 2GB if space is needed it can be cleared ``` bash (nostr) ever3st@Alashazam:~/Documents/dev/python/$ pip cache purge Files removed: 273 (nostr) ever3st@Alashazam:~/Documents/dev/python/bots/nostr$ pip cache info Package index page cache location: /home/ever3st/.cache/pip/http Package index page cache size: 0 bytes Number of HTTP files: 0 Wheels location: /home/ever3st/.cache/pip/wheels Wheels size: 326 bytes Number of wheels: 0 ``` @ 6538925e:571e55c3
2025-02-13 16:05:42\ **Nostr Live Streams (Beta)** If you follow shows like Rabbit Hole Recap, THE Bitcoin Podcast or Simply Bitcoin on Nostr, you can now watch the video in Fountain and hang out in the live chat as it’s being recorded. You'll find livestreams from people who follow on Nostr at the top of the home screen. As well and live podcasts, you will also find live music events from PhantomPowerMedia, radio stations like NoGood and Noderunners, as well as channels dedicated to gaming, art, coding and much more. Bringing creators and fans together through live experiences enables audience participation and creates a special feeling of community, so we’re really excited to get this into your hands. Nostr livestreams are a beta feature - i.e. we still have a lot more work to do! We will continue to make improvements to livestreams over the coming months - so we would love to hear your feedback. \ **Storage Manager** We’ve added a storage manager in the app’s settings so that you can view file storage size for audio downloads, video downloads, transcripts, image cache, feed cache, and temp files. You can delete all files in any of these folders to free up storage on your device so that Fountain continues to run optimally. There are other performance and stability improvements that we are working on too. For example, in the next couple of weeks we will be rolling out an image proxy service, which should reduce mobile data usage and optimise storage. Stay tuned for further updates and, as always, thanks for your support.
@ 6538925e:571e55c3
2025-02-13 16:05:42\ **Nostr Live Streams (Beta)** If you follow shows like Rabbit Hole Recap, THE Bitcoin Podcast or Simply Bitcoin on Nostr, you can now watch the video in Fountain and hang out in the live chat as it’s being recorded. You'll find livestreams from people who follow on Nostr at the top of the home screen. As well and live podcasts, you will also find live music events from PhantomPowerMedia, radio stations like NoGood and Noderunners, as well as channels dedicated to gaming, art, coding and much more. Bringing creators and fans together through live experiences enables audience participation and creates a special feeling of community, so we’re really excited to get this into your hands. Nostr livestreams are a beta feature - i.e. we still have a lot more work to do! We will continue to make improvements to livestreams over the coming months - so we would love to hear your feedback. \ **Storage Manager** We’ve added a storage manager in the app’s settings so that you can view file storage size for audio downloads, video downloads, transcripts, image cache, feed cache, and temp files. You can delete all files in any of these folders to free up storage on your device so that Fountain continues to run optimally. There are other performance and stability improvements that we are working on too. For example, in the next couple of weeks we will be rolling out an image proxy service, which should reduce mobile data usage and optimise storage. Stay tuned for further updates and, as always, thanks for your support. @ f1989a96:bcaaf2c1
2025-02-13 14:24:32Good morning, readers! This week, we highlight how authoritarian regimes are manipulating digital assets. The Central African Republic launched a government-backed meme coin that crashed spectacularly within a day of launch as regime insiders cashed out for profits, leaving the public with worthless tokens. Meanwhile, the Nigerian regime introduced its first official stablecoin, cNGN. It is issued by the African Stablecoin Consortium and is backed 1:1 with the naira. Still, it operates under the direct oversight of the Nigerian Securities and Exchange Commission, allowing further surveillance of Nigerians’ financial activity alongside the struggling eNaira CBDC. On the freedom tech front, Mullad VPN now supports Bitcoin payments via the Lightning Network, offering activists, journalists, and individuals under oppressive regimes a censorship-resistant and permissionless way to pay for their privacy. Additionally, SeedSigner, an open-source hardware wallet for Bitcoin self-custody, rolled out multilingual support, expanding accessibility to Spanish-speaking activists and human rights defenders.\ \ Finally, journalist Frank Corva explores Africa’s grassroots Bitcoin movement, where open-source tools and circular economies are empowering communities inside authoritarian regimes with financial freedom. For those who doubt Bitcoin’s real-world impact, this article is a must-read. **Now, let’s get right to it!** ### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Central African Republic | Launches Meme Coin Experiment** The Central African Republic (CAR) [debuted](https://www.reuters.com/world/africa/central-african-republic-debuts-meme-coin-experiment-2025-02-10/) a government-backed meme coin, $CAR, which President Faustin-Archange Touadéra [claims](https://www.reuters.com/world/africa/central-african-republic-debuts-meme-coin-experiment-2025-02-10/) will “unite people” and “support national development.” In reality, meme coins are speculative assets that often serve as vehicles for insider profit. This scheme follows CAR’s failed [Sango Coin](https://www.mariblock.com/central-african-republic-top-court-rules-sango-coin-unconstitutional/) project, which promised citizenship and land in exchange for [locked](https://www.mariblock.com/central-african-republic-top-court-rules-sango-coin-unconstitutional/) investments but sold only 7.5% of its supply. Those who did “buy in” did not receive what was promised. In 2022, CAR briefly made Bitcoin legal tender, calling it a path to sovereignty — only to [abandon](https://bitcoinmagazine.com/culture/why-bitcoin-failed-in-car) it shortly after. Instead of supporting open and neutral money like Bitcoin, the government has turned to dubious crypto schemes. The real beneficiaries of $CAR appear to be regime insiders who reportedly cashed out [$40 million](https://x.com/bored2boar/status/1889002901370196098) while the public holds [worthless](https://decrypt.co/305225/central-african-republic-president-meme-coin) tokens. #### **Nigeria | Debuts Naira Stablecoin** The Nigerian state [launched](https://www.mariblock.com/move-over-enaira-cngn-enters-the-chat-2/) its first regulated stablecoin, [cNGN](https://cngn.co/?ref=mariblock.com). Similar to US dollar-pegged stablecoins like USDT and USDC, cNGN is pegged 1:1 to its local currency (the naira). It is issued by the African Stablecoin Consortium (ASC), a private coalition of Nigerian financial institutions and blockchain companies. Positioned as a bridge between fiat and digital assets, cNGN aims to facilitate remittances and trade but comes with strict verification requirements that limit financial privacy. The Nigerian SEC also tightly regulates the stablecoin and it is only available on government-approved exchanges, Busha and Quidax. As Nigeria expands its control over digital transactions — through both cNGN and its struggling [eNaira CBDC](https://cbdctracker.hrf.org/currency/nigeria) — more and more Nigerians are [turning](https://www.forbes.com/sites/digital-assets/2024/01/08/central-bank-of-nigeria-approves-naira-stablecoin-for-2024-launch/) to Bitcoin as a censorship-resistant alternative. #### **Russia | Proposes Registry to Track Bitcoin Mining Hardware** Russia’s deputy energy minister, Yevgeny Grabchak, has [proposed](https://theminermag.com/news/2025-02-03/russia-minister-bitcoin-miner/) a centralized registry of Bitcoin mining equipment and wallet addresses to “identify mining activities and ensure stricter enforcement of bans in restricted regions,” such as Russian-occupied Ukraine territories. Meanwhile, the Chairman of the State Duma Committee on Energy, Nikolai Shulginov, warned that last year’s mining ban in several Russian and occupied regions may not be enough to eliminate mining fully. As an authoritarian state with an egregious human rights record and a long history of financial repression, Russia appears intent on tightening surveillance of economic activity — especially that of Bitcoin. By registering, tracking, and restricting mining, the Kremlin expands its financial control, undermines economic autonomy, and limits access to permissionless money. #### **Turkey | Erdoğan Targets Opposition as Inflation Forecast Rises** Turkish President Recep Tayyip Erdoğan sentenced Istanbul Mayor Ekrem Imamoglu — a key political rival — to [seven](https://www.bloomberg.com/news/articles/2025-02-05/turkey-s-main-rival-to-erdogan-faces-jail-time-in-new-indictment) years in prison on charges widely seen as politically motivated. If upheld, the conviction will bar Imamoglu from office, further clearing Erdoğan’s path to dominance ahead of the 2028 elections. At the same time, Turkey’s economic crisis is worsening. [Accelerating inflation](https://www.reuters.com/world/middle-east/turkey-cenbank-raises-inflation-forecast-says-not-autopilot-with-cuts-2025-02-07/) forced the central bank to raise its 2025 forecast from 21% to 24%, exacerbating the lira’s decline and eroding purchasing power. As both political and financial repression deepen, more Turks are turning to alternatives to sidestep Erdoğan’s expanding control over the economic and political sphere. #### **Georgia | Regime to Pass Censorship Law** Georgia’s ruling Georgian Dream party is set to introduce a media censorship [law](https://jam-news.net/georgian-dream-plans-to-pass-media-censorship-law/) aimed at enforcing government-defined standards for journalistic objectivity and ethics, while also restricting foreign funding for media outlets. MP Mamuka Mdinaradze [claims](https://jam-news.net/ngos-and-media-organizations-of-georgia-to-challenge-the-foreign-agents-law-in-strasbourg-court/) the law will establish monitoring mechanisms and is modeled after UK regulations, though critics [compare](https://jam-news.net/opinion-ivanishvili-adopts-belarusian-tactics-to-control-protests/) it to Belarusian-style repression. Georgian Dream Prime Minister Irakli Kobakhidze defended the move as necessary to close legislative “loopholes” and strengthen state control. Journalists and activists warn that the law is part of a broader crackdown on press freedom and dissent. Decentralized social networks like Nostr will become increasingly vital for journalists and activists to communicate freely, resist censorship, and ensure the flow of independent information. \___________________________________________________________\_ #### **Webinar Series for Nonprofits: Become Unstoppable** HRF will host a [free, three-day webinar](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform) from March 17-19, teaching human rights defenders and nonprofits how to use Bitcoin to counter state censorship and confiscation. Sessions run daily from 10:30 a.m. to 12:00 p.m. EDT and are beginner-friendly. The webinar will be led by Anna Chekhovich, HRF’s Bitcoin nonprofit adoption lead and financial manager at Alexei Navalny’s Anti-Corruption Foundation. ### [Register Here](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform) #### **SXSW | The Human Rights Risks of Central Bank Digital Currencies (CBDCs)** Join HRF at [SXSW 2025](https://www.sxsw.com/) in Austin from March 9-12 to explore how CBDCs threaten financial freedom. Experts [Roger Huang](https://x.com/Rogerh1991), [Charlene Fadirepo](https://x.com/CharFadirepo), and [Nick Anthony](https://x.com/EconWithNick) will discuss how authoritarian regimes use CBDCs for surveillance and control on March 9. Attendees can also visit HRF’s [CBDC Tracker](https://cbdctracker.hrf.org/) booth to explore an interactive map of CBDC developments worldwide. ### [Get Tickets](https://www.sxsw.com/conference/) \___________________________________________________________\_ ## BITCOIN AND FREEDOM TECH NEWS #### **Mullvad VPN | Testing Lightning Network Payments** [Mullvad VPN](https://mullvad.net/en) is experimenting with Bitcoin for payments via the Lightning Network, a second-layer payment protocol built on Bitcoin that enables faster, cheaper, and more private transactions. This integration lets Mullvad VPN users pay for their services in bitcoin while enhancing their privacy and bypassing payment networks that track or censor financial activity. VPNs protect users by masking IP addresses and encrypting traffic. Accepting Bitcoin over Lightning strengthens this protection with a censorship-resistant payment option. For activists, journalists, and individuals in authoritarian regimes, this combination provides a shield against surveillance. #### **SeedSigner | Releases Multilingual Support** [SeedSigner](https://seedsigner.com/), an open-source and customizable Bitcoin hardware wallet and HRF grantee, [introduced](https://github.com/SeedSigner/seedsigner/releases/tag/0.8.5) multilingual support for Spanish. This update makes secure Bitcoin self-custody more accessible to Spanish-speaking activists and human rights defenders who may rely on Bitcoin for transactional freedom. By expanding access to secure self-custody, SeedSigner helps reduce dependence on restrictive financial systems and allows more people in Nicaragua, Venezuela, Cuba, and beyond to “be their own bank.” #### **Iris | Implements Private Bitcoin Payments with Cashu** [Iris](https://iris.cx/), a Nostr client, has added support for a Cashu wallet to allow users to send and receive ecash. Cashu is an open-source Chaumian ecash protocol built for Bitcoin and integrated with the Lightning Network. It lets users make fast, low-cost, and extremely private transactions using Bitcoin-backed ecash. While it requires a trusted custodian, it helps users spend Bitcoin anonymously without revealing their identity or transaction activity. This ability provides activists and nonprofits a different way to make private Bitcoin payments alongside nostr’s censorship-resistant communications. #### **Sparrow Wallet | Supports Lark for USB Hardware Wallets** [Sparrow Wallet](https://sparrowwallet.com/), a popular open-source Bitcoin wallet, has added support for [Lark](https://github.com/sparrowwallet/larkapp?mc_cid=aab08acf41&mc_eid=5c5878c08e), a new tool for USB hardware wallet communication. Lark works alongside the existing [Hardware Wallet Interface](https://github.com/bitcoin-core/HWI) (HWI), giving users an alternative way to connect their hardware wallets via USB. This update improves reliability, reduces dependence on a single software interface, and strengthens Bitcoin self-custody. #### **Bitcoin Dada | Opens Applications for Second Cohort of Dada Devs** [Bitcoin Dada](https://btcdada.com/), an HRF-supported nonprofit initiative empowering African women through Bitcoin and financial education, is now [accepting](https://x.com/DadaDevs/status/1886819762660929674) applications for the second cohort of Dada Devs. This developer program provides hands-on training, mentorship, and a collaborative community to help African women under authoritarian regimes contribute to Bitcoin development. If you’re an aspiring female developer, [apply now](https://docs.google.com/forms/d/e/1FAIpQLSeJ8nXL96qNeCAaXnSlGxqykBPEGm21z9qS9oE1ldNusM0nTA/viewform) to join a network of African women shaping the future of finance. Applications close Feb. 13. #### **Summer of Bitcoin | Applications for Summer 2025 Cohort Now Open** [Summer of Bitcoin](https://www.summerofbitcoin.org/), an HRF-supported Bitcoin internship program, is now accepting [applications](https://www.summerofbitcoin.org/apply) for its summer 2025 cohort. This program introduces students from anywhere, including from authoritarian regimes, to Bitcoin open-source development and design, giving interns the option to choose between a developer or designer track based on their interests. Participants will gain hands-on work experience, contribute to real-world Bitcoin projects, and receive mentorship from industry leaders. You can learn more and apply [here](https://www.summerofbitcoin.org/). #### **Spiral | Announces Grant Renewals for the Bitcoin Design Community and BDK** [Spiral](http://spiral.xyz), a Bitcoin company building and funding open-source projects, announced renewed grants for critical initiatives, including the [Bitcoin Design Community](https://github.com/bitcoindesign) and [Bitcoin Dev Kit](https://bitcoindevkit.org/) (BDK). The Bitcoin Design Community is a free and open-source resource for designers, developers, and others working on non-custodial Bitcoin products. This [grant](https://x.com/spiralbtc/status/1885000120439095607) will support designers who push the user experience and adoption of Bitcoin forward. Meanwhile, BDK is a software library that helps developers in building cross-platform Bitcoin wallets. Its [grant](https://x.com/spiralbtc/status/1884998758976405840) will support the project’s continued refinement and development. ## RECOMMENDED CONTENT #### **The Bitcoin and Cypherpunk Spirit Is Alive and Well in Africa by Frank Corva** In this [article](https://bitcoinmagazine.com/culture/the-bitcoin-and-cypherpunk-spirit-is-alive-and-well-in-africa) for [Bitcoin Magazine](http://bitcoinmagazine.com), journalist [Frank Corva](https://x.com/frankcorva) spotlights Bitcoin's growing presence across Africa. Across the continent, people are building Bitcoin circular economies, open-source financial tools, and educational initiatives. From [Bitcoin Ekasi](https://x.com/BitcoinEkasi) in South Africa to [AfriBit Kibera](https://x.com/AfribitKibera) in Kenya and [Bitcoin Dua](https://x.com/bitcoin_dua) in Ghana, these grassroots initiatives drive financial inclusion and education for individuals and communities. Meanwhile, tools like [Tando](https://tando.me/) and [Machankura](https://8333.mobi/) are expanding access to transactional freedom, and conferences like [Adopting Bitcoin Captetown](https://za25.adoptingbitcoin.org/) and the [Africa Bitcoin Conference](https://afrobitcoin.org/) nurture ongoing collaboration between individuals, developers, and activists to advance financial freedom on a continent that otherwise has very little liberal democracy. Read the full article [here](https://bitcoinmagazine.com/culture/the-bitcoin-and-cypherpunk-spirit-is-alive-and-well-in-africa). #### **Using Bitcoin Without Internet! Here’s How Machankura Makes It Happen with Anita Posch** In this short [interview](https://www.youtube.com/watch?v=XzXfd237XVo), Bitcoin educator and host of the [Bitcoin for Fairness](https://www.youtube.com/@AnitaPosch) channel, Anita Posch, speaks with Mary Imasuen, a [Machankura](https://8333.mobi/) team member, about how this technology makes Bitcoin accessible to Africans without Internet access. Machankura is an app that allows feature phones to send and receive Bitcoin using the Unstructured Supplementary Service Data (USSD) protocol, a mobile communications system similar to SMS. This means people can transact in Bitcoin without needing a smartphone or data connection, a situation common to many living under autocratic regimes in sub-Saharan Africa. By removing Internet barriers, Machankura helps millions of Africans overcome high data costs and unreliable networks, offering a practical solution to financial inclusion. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/)
@ f1989a96:bcaaf2c1
2025-02-13 14:24:32Good morning, readers! This week, we highlight how authoritarian regimes are manipulating digital assets. The Central African Republic launched a government-backed meme coin that crashed spectacularly within a day of launch as regime insiders cashed out for profits, leaving the public with worthless tokens. Meanwhile, the Nigerian regime introduced its first official stablecoin, cNGN. It is issued by the African Stablecoin Consortium and is backed 1:1 with the naira. Still, it operates under the direct oversight of the Nigerian Securities and Exchange Commission, allowing further surveillance of Nigerians’ financial activity alongside the struggling eNaira CBDC. On the freedom tech front, Mullad VPN now supports Bitcoin payments via the Lightning Network, offering activists, journalists, and individuals under oppressive regimes a censorship-resistant and permissionless way to pay for their privacy. Additionally, SeedSigner, an open-source hardware wallet for Bitcoin self-custody, rolled out multilingual support, expanding accessibility to Spanish-speaking activists and human rights defenders.\ \ Finally, journalist Frank Corva explores Africa’s grassroots Bitcoin movement, where open-source tools and circular economies are empowering communities inside authoritarian regimes with financial freedom. For those who doubt Bitcoin’s real-world impact, this article is a must-read. **Now, let’s get right to it!** ### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Central African Republic | Launches Meme Coin Experiment** The Central African Republic (CAR) [debuted](https://www.reuters.com/world/africa/central-african-republic-debuts-meme-coin-experiment-2025-02-10/) a government-backed meme coin, $CAR, which President Faustin-Archange Touadéra [claims](https://www.reuters.com/world/africa/central-african-republic-debuts-meme-coin-experiment-2025-02-10/) will “unite people” and “support national development.” In reality, meme coins are speculative assets that often serve as vehicles for insider profit. This scheme follows CAR’s failed [Sango Coin](https://www.mariblock.com/central-african-republic-top-court-rules-sango-coin-unconstitutional/) project, which promised citizenship and land in exchange for [locked](https://www.mariblock.com/central-african-republic-top-court-rules-sango-coin-unconstitutional/) investments but sold only 7.5% of its supply. Those who did “buy in” did not receive what was promised. In 2022, CAR briefly made Bitcoin legal tender, calling it a path to sovereignty — only to [abandon](https://bitcoinmagazine.com/culture/why-bitcoin-failed-in-car) it shortly after. Instead of supporting open and neutral money like Bitcoin, the government has turned to dubious crypto schemes. The real beneficiaries of $CAR appear to be regime insiders who reportedly cashed out [$40 million](https://x.com/bored2boar/status/1889002901370196098) while the public holds [worthless](https://decrypt.co/305225/central-african-republic-president-meme-coin) tokens. #### **Nigeria | Debuts Naira Stablecoin** The Nigerian state [launched](https://www.mariblock.com/move-over-enaira-cngn-enters-the-chat-2/) its first regulated stablecoin, [cNGN](https://cngn.co/?ref=mariblock.com). Similar to US dollar-pegged stablecoins like USDT and USDC, cNGN is pegged 1:1 to its local currency (the naira). It is issued by the African Stablecoin Consortium (ASC), a private coalition of Nigerian financial institutions and blockchain companies. Positioned as a bridge between fiat and digital assets, cNGN aims to facilitate remittances and trade but comes with strict verification requirements that limit financial privacy. The Nigerian SEC also tightly regulates the stablecoin and it is only available on government-approved exchanges, Busha and Quidax. As Nigeria expands its control over digital transactions — through both cNGN and its struggling [eNaira CBDC](https://cbdctracker.hrf.org/currency/nigeria) — more and more Nigerians are [turning](https://www.forbes.com/sites/digital-assets/2024/01/08/central-bank-of-nigeria-approves-naira-stablecoin-for-2024-launch/) to Bitcoin as a censorship-resistant alternative. #### **Russia | Proposes Registry to Track Bitcoin Mining Hardware** Russia’s deputy energy minister, Yevgeny Grabchak, has [proposed](https://theminermag.com/news/2025-02-03/russia-minister-bitcoin-miner/) a centralized registry of Bitcoin mining equipment and wallet addresses to “identify mining activities and ensure stricter enforcement of bans in restricted regions,” such as Russian-occupied Ukraine territories. Meanwhile, the Chairman of the State Duma Committee on Energy, Nikolai Shulginov, warned that last year’s mining ban in several Russian and occupied regions may not be enough to eliminate mining fully. As an authoritarian state with an egregious human rights record and a long history of financial repression, Russia appears intent on tightening surveillance of economic activity — especially that of Bitcoin. By registering, tracking, and restricting mining, the Kremlin expands its financial control, undermines economic autonomy, and limits access to permissionless money. #### **Turkey | Erdoğan Targets Opposition as Inflation Forecast Rises** Turkish President Recep Tayyip Erdoğan sentenced Istanbul Mayor Ekrem Imamoglu — a key political rival — to [seven](https://www.bloomberg.com/news/articles/2025-02-05/turkey-s-main-rival-to-erdogan-faces-jail-time-in-new-indictment) years in prison on charges widely seen as politically motivated. If upheld, the conviction will bar Imamoglu from office, further clearing Erdoğan’s path to dominance ahead of the 2028 elections. At the same time, Turkey’s economic crisis is worsening. [Accelerating inflation](https://www.reuters.com/world/middle-east/turkey-cenbank-raises-inflation-forecast-says-not-autopilot-with-cuts-2025-02-07/) forced the central bank to raise its 2025 forecast from 21% to 24%, exacerbating the lira’s decline and eroding purchasing power. As both political and financial repression deepen, more Turks are turning to alternatives to sidestep Erdoğan’s expanding control over the economic and political sphere. #### **Georgia | Regime to Pass Censorship Law** Georgia’s ruling Georgian Dream party is set to introduce a media censorship [law](https://jam-news.net/georgian-dream-plans-to-pass-media-censorship-law/) aimed at enforcing government-defined standards for journalistic objectivity and ethics, while also restricting foreign funding for media outlets. MP Mamuka Mdinaradze [claims](https://jam-news.net/ngos-and-media-organizations-of-georgia-to-challenge-the-foreign-agents-law-in-strasbourg-court/) the law will establish monitoring mechanisms and is modeled after UK regulations, though critics [compare](https://jam-news.net/opinion-ivanishvili-adopts-belarusian-tactics-to-control-protests/) it to Belarusian-style repression. Georgian Dream Prime Minister Irakli Kobakhidze defended the move as necessary to close legislative “loopholes” and strengthen state control. Journalists and activists warn that the law is part of a broader crackdown on press freedom and dissent. Decentralized social networks like Nostr will become increasingly vital for journalists and activists to communicate freely, resist censorship, and ensure the flow of independent information. \___________________________________________________________\_ #### **Webinar Series for Nonprofits: Become Unstoppable** HRF will host a [free, three-day webinar](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform) from March 17-19, teaching human rights defenders and nonprofits how to use Bitcoin to counter state censorship and confiscation. Sessions run daily from 10:30 a.m. to 12:00 p.m. EDT and are beginner-friendly. The webinar will be led by Anna Chekhovich, HRF’s Bitcoin nonprofit adoption lead and financial manager at Alexei Navalny’s Anti-Corruption Foundation. ### [Register Here](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform) #### **SXSW | The Human Rights Risks of Central Bank Digital Currencies (CBDCs)** Join HRF at [SXSW 2025](https://www.sxsw.com/) in Austin from March 9-12 to explore how CBDCs threaten financial freedom. Experts [Roger Huang](https://x.com/Rogerh1991), [Charlene Fadirepo](https://x.com/CharFadirepo), and [Nick Anthony](https://x.com/EconWithNick) will discuss how authoritarian regimes use CBDCs for surveillance and control on March 9. Attendees can also visit HRF’s [CBDC Tracker](https://cbdctracker.hrf.org/) booth to explore an interactive map of CBDC developments worldwide. ### [Get Tickets](https://www.sxsw.com/conference/) \___________________________________________________________\_ ## BITCOIN AND FREEDOM TECH NEWS #### **Mullvad VPN | Testing Lightning Network Payments** [Mullvad VPN](https://mullvad.net/en) is experimenting with Bitcoin for payments via the Lightning Network, a second-layer payment protocol built on Bitcoin that enables faster, cheaper, and more private transactions. This integration lets Mullvad VPN users pay for their services in bitcoin while enhancing their privacy and bypassing payment networks that track or censor financial activity. VPNs protect users by masking IP addresses and encrypting traffic. Accepting Bitcoin over Lightning strengthens this protection with a censorship-resistant payment option. For activists, journalists, and individuals in authoritarian regimes, this combination provides a shield against surveillance. #### **SeedSigner | Releases Multilingual Support** [SeedSigner](https://seedsigner.com/), an open-source and customizable Bitcoin hardware wallet and HRF grantee, [introduced](https://github.com/SeedSigner/seedsigner/releases/tag/0.8.5) multilingual support for Spanish. This update makes secure Bitcoin self-custody more accessible to Spanish-speaking activists and human rights defenders who may rely on Bitcoin for transactional freedom. By expanding access to secure self-custody, SeedSigner helps reduce dependence on restrictive financial systems and allows more people in Nicaragua, Venezuela, Cuba, and beyond to “be their own bank.” #### **Iris | Implements Private Bitcoin Payments with Cashu** [Iris](https://iris.cx/), a Nostr client, has added support for a Cashu wallet to allow users to send and receive ecash. Cashu is an open-source Chaumian ecash protocol built for Bitcoin and integrated with the Lightning Network. It lets users make fast, low-cost, and extremely private transactions using Bitcoin-backed ecash. While it requires a trusted custodian, it helps users spend Bitcoin anonymously without revealing their identity or transaction activity. This ability provides activists and nonprofits a different way to make private Bitcoin payments alongside nostr’s censorship-resistant communications. #### **Sparrow Wallet | Supports Lark for USB Hardware Wallets** [Sparrow Wallet](https://sparrowwallet.com/), a popular open-source Bitcoin wallet, has added support for [Lark](https://github.com/sparrowwallet/larkapp?mc_cid=aab08acf41&mc_eid=5c5878c08e), a new tool for USB hardware wallet communication. Lark works alongside the existing [Hardware Wallet Interface](https://github.com/bitcoin-core/HWI) (HWI), giving users an alternative way to connect their hardware wallets via USB. This update improves reliability, reduces dependence on a single software interface, and strengthens Bitcoin self-custody. #### **Bitcoin Dada | Opens Applications for Second Cohort of Dada Devs** [Bitcoin Dada](https://btcdada.com/), an HRF-supported nonprofit initiative empowering African women through Bitcoin and financial education, is now [accepting](https://x.com/DadaDevs/status/1886819762660929674) applications for the second cohort of Dada Devs. This developer program provides hands-on training, mentorship, and a collaborative community to help African women under authoritarian regimes contribute to Bitcoin development. If you’re an aspiring female developer, [apply now](https://docs.google.com/forms/d/e/1FAIpQLSeJ8nXL96qNeCAaXnSlGxqykBPEGm21z9qS9oE1ldNusM0nTA/viewform) to join a network of African women shaping the future of finance. Applications close Feb. 13. #### **Summer of Bitcoin | Applications for Summer 2025 Cohort Now Open** [Summer of Bitcoin](https://www.summerofbitcoin.org/), an HRF-supported Bitcoin internship program, is now accepting [applications](https://www.summerofbitcoin.org/apply) for its summer 2025 cohort. This program introduces students from anywhere, including from authoritarian regimes, to Bitcoin open-source development and design, giving interns the option to choose between a developer or designer track based on their interests. Participants will gain hands-on work experience, contribute to real-world Bitcoin projects, and receive mentorship from industry leaders. You can learn more and apply [here](https://www.summerofbitcoin.org/). #### **Spiral | Announces Grant Renewals for the Bitcoin Design Community and BDK** [Spiral](http://spiral.xyz), a Bitcoin company building and funding open-source projects, announced renewed grants for critical initiatives, including the [Bitcoin Design Community](https://github.com/bitcoindesign) and [Bitcoin Dev Kit](https://bitcoindevkit.org/) (BDK). The Bitcoin Design Community is a free and open-source resource for designers, developers, and others working on non-custodial Bitcoin products. This [grant](https://x.com/spiralbtc/status/1885000120439095607) will support designers who push the user experience and adoption of Bitcoin forward. Meanwhile, BDK is a software library that helps developers in building cross-platform Bitcoin wallets. Its [grant](https://x.com/spiralbtc/status/1884998758976405840) will support the project’s continued refinement and development. ## RECOMMENDED CONTENT #### **The Bitcoin and Cypherpunk Spirit Is Alive and Well in Africa by Frank Corva** In this [article](https://bitcoinmagazine.com/culture/the-bitcoin-and-cypherpunk-spirit-is-alive-and-well-in-africa) for [Bitcoin Magazine](http://bitcoinmagazine.com), journalist [Frank Corva](https://x.com/frankcorva) spotlights Bitcoin's growing presence across Africa. Across the continent, people are building Bitcoin circular economies, open-source financial tools, and educational initiatives. From [Bitcoin Ekasi](https://x.com/BitcoinEkasi) in South Africa to [AfriBit Kibera](https://x.com/AfribitKibera) in Kenya and [Bitcoin Dua](https://x.com/bitcoin_dua) in Ghana, these grassroots initiatives drive financial inclusion and education for individuals and communities. Meanwhile, tools like [Tando](https://tando.me/) and [Machankura](https://8333.mobi/) are expanding access to transactional freedom, and conferences like [Adopting Bitcoin Captetown](https://za25.adoptingbitcoin.org/) and the [Africa Bitcoin Conference](https://afrobitcoin.org/) nurture ongoing collaboration between individuals, developers, and activists to advance financial freedom on a continent that otherwise has very little liberal democracy. Read the full article [here](https://bitcoinmagazine.com/culture/the-bitcoin-and-cypherpunk-spirit-is-alive-and-well-in-africa). #### **Using Bitcoin Without Internet! Here’s How Machankura Makes It Happen with Anita Posch** In this short [interview](https://www.youtube.com/watch?v=XzXfd237XVo), Bitcoin educator and host of the [Bitcoin for Fairness](https://www.youtube.com/@AnitaPosch) channel, Anita Posch, speaks with Mary Imasuen, a [Machankura](https://8333.mobi/) team member, about how this technology makes Bitcoin accessible to Africans without Internet access. Machankura is an app that allows feature phones to send and receive Bitcoin using the Unstructured Supplementary Service Data (USSD) protocol, a mobile communications system similar to SMS. This means people can transact in Bitcoin without needing a smartphone or data connection, a situation common to many living under autocratic regimes in sub-Saharan Africa. By removing Internet barriers, Machankura helps millions of Africans overcome high data costs and unreliable networks, offering a practical solution to financial inclusion. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/) @ 1c197b12:242e1642
2025-02-09 22:56:33A Cypherpunk's Manifesto by Eric Hughes Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world. If two parties have some sort of dealings, then each has a memory of their interaction. Each party can speak about their own memory of this; how could anyone prevent it? One could pass laws against it, but the freedom of speech, even more than privacy, is fundamental to an open society; we seek not to restrict any speech at all. If many parties speak together in the same forum, each can speak to all the others and aggregate together knowledge about individuals and other parties. The power of electronic communications has enabled such group speech, and it will not go away merely because we might want it to. Since we desire privacy, we must ensure that each party to a transaction have knowledge only of that which is directly necessary for that transaction. Since any information can be spoken of, we must ensure that we reveal as little as possible. In most cases personal identity is not salient. When I purchase a magazine at a store and hand cash to the clerk, there is no need to know who I am. When I ask my electronic mail provider to send and receive messages, my provider need not know to whom I am speaking or what I am saying or what others are saying to me; my provider only need know how to get the message there and how much I owe them in fees. When my identity is revealed by the underlying mechanism of the transaction, I have no privacy. I cannot here selectively reveal myself; I must always reveal myself. Therefore, privacy in an open society requires anonymous transaction systems. Until now, cash has been the primary such system. An anonymous transaction system is not a secret transaction system. An anonymous system empowers individuals to reveal their identity when desired and only when desired; this is the essence of privacy. Privacy in an open society also requires cryptography. If I say something, I want it heard only by those for whom I intend it. If the content of my speech is available to the world, I have no privacy. To encrypt is to indicate the desire for privacy, and to encrypt with weak cryptography is to indicate not too much desire for privacy. Furthermore, to reveal one's identity with assurance when the default is anonymity requires the cryptographic signature. We cannot expect governments, corporations, or other large, faceless organizations to grant us privacy out of their beneficence. It is to their advantage to speak of us, and we should expect that they will speak. To try to prevent their speech is to fight against the realities of information. Information does not just want to be free, it longs to be free. Information expands to fill the available storage space. Information is Rumor's younger, stronger cousin; Information is fleeter of foot, has more eyes, knows more, and understands less than Rumor. We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do. We the Cypherpunks are dedicated to building anonymous systems. We are defending our privacy with cryptography, with anonymous mail forwarding systems, with digital signatures, and with electronic money. Cypherpunks write code. We know that someone has to write software to defend privacy, and since we can't get privacy unless we all do, we're going to write it. We publish our code so that our fellow Cypherpunks may practice and play with it. Our code is free for all to use, worldwide. We don't much care if you don't approve of the software we write. We know that software can't be destroyed and that a widely dispersed system can't be shut down. Cypherpunks deplore regulations on cryptography, for encryption is fundamentally a private act. The act of encryption, in fact, removes information from the public realm. Even laws against cryptography reach only so far as a nation's border and the arm of its violence. Cryptography will ineluctably spread over the whole globe, and with it the anonymous transactions systems that it makes possible. For privacy to be widespread it must be part of a social contract. People must come and together deploy these systems for the common good. Privacy only extends so far as the cooperation of one's fellows in society. We the Cypherpunks seek your questions and your concerns and hope we may engage you so that we do not deceive ourselves. We will not, however, be moved out of our course because some may disagree with our goals. The Cypherpunks are actively engaged in making the networks safer for privacy. Let us proceed together apace. Onward. Eric Hughes <hughes@soda.berkeley.edu> 9 March 1993
@ 1c197b12:242e1642
2025-02-09 22:56:33A Cypherpunk's Manifesto by Eric Hughes Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world. If two parties have some sort of dealings, then each has a memory of their interaction. Each party can speak about their own memory of this; how could anyone prevent it? One could pass laws against it, but the freedom of speech, even more than privacy, is fundamental to an open society; we seek not to restrict any speech at all. If many parties speak together in the same forum, each can speak to all the others and aggregate together knowledge about individuals and other parties. The power of electronic communications has enabled such group speech, and it will not go away merely because we might want it to. Since we desire privacy, we must ensure that each party to a transaction have knowledge only of that which is directly necessary for that transaction. Since any information can be spoken of, we must ensure that we reveal as little as possible. In most cases personal identity is not salient. When I purchase a magazine at a store and hand cash to the clerk, there is no need to know who I am. When I ask my electronic mail provider to send and receive messages, my provider need not know to whom I am speaking or what I am saying or what others are saying to me; my provider only need know how to get the message there and how much I owe them in fees. When my identity is revealed by the underlying mechanism of the transaction, I have no privacy. I cannot here selectively reveal myself; I must always reveal myself. Therefore, privacy in an open society requires anonymous transaction systems. Until now, cash has been the primary such system. An anonymous transaction system is not a secret transaction system. An anonymous system empowers individuals to reveal their identity when desired and only when desired; this is the essence of privacy. Privacy in an open society also requires cryptography. If I say something, I want it heard only by those for whom I intend it. If the content of my speech is available to the world, I have no privacy. To encrypt is to indicate the desire for privacy, and to encrypt with weak cryptography is to indicate not too much desire for privacy. Furthermore, to reveal one's identity with assurance when the default is anonymity requires the cryptographic signature. We cannot expect governments, corporations, or other large, faceless organizations to grant us privacy out of their beneficence. It is to their advantage to speak of us, and we should expect that they will speak. To try to prevent their speech is to fight against the realities of information. Information does not just want to be free, it longs to be free. Information expands to fill the available storage space. Information is Rumor's younger, stronger cousin; Information is fleeter of foot, has more eyes, knows more, and understands less than Rumor. We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do. We the Cypherpunks are dedicated to building anonymous systems. We are defending our privacy with cryptography, with anonymous mail forwarding systems, with digital signatures, and with electronic money. Cypherpunks write code. We know that someone has to write software to defend privacy, and since we can't get privacy unless we all do, we're going to write it. We publish our code so that our fellow Cypherpunks may practice and play with it. Our code is free for all to use, worldwide. We don't much care if you don't approve of the software we write. We know that software can't be destroyed and that a widely dispersed system can't be shut down. Cypherpunks deplore regulations on cryptography, for encryption is fundamentally a private act. The act of encryption, in fact, removes information from the public realm. Even laws against cryptography reach only so far as a nation's border and the arm of its violence. Cryptography will ineluctably spread over the whole globe, and with it the anonymous transactions systems that it makes possible. For privacy to be widespread it must be part of a social contract. People must come and together deploy these systems for the common good. Privacy only extends so far as the cooperation of one's fellows in society. We the Cypherpunks seek your questions and your concerns and hope we may engage you so that we do not deceive ourselves. We will not, however, be moved out of our course because some may disagree with our goals. The Cypherpunks are actively engaged in making the networks safer for privacy. Let us proceed together apace. Onward. Eric Hughes <hughes@soda.berkeley.edu> 9 March 1993 @ 9673b322:1b75ee9e
2025-02-13 14:15:38This is test content 
@ 9673b322:1b75ee9e
2025-02-13 14:15:38This is test content  @ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content. ## Key Features: ### Video Processing: - Automatically downloads YouTube videos, transcripts, and chapter information - Splits transcripts into sections based on video chapters ### Content Summarization: - Utilizes language models to transform spoken content into clear, readable text - Formats output in AsciiDoc for improved readability and navigation - Highlights key terms and concepts with [[term]] notation for potential cross-referencing ### Diagram Extraction: - Analyzes video entropy to identify static diagram/slide sections - Provides a user-friendly GUI for manual selection of relevant time ranges - Allows users to pick representative frames from selected ranges ## Going Forward: Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care. While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs. ## Screenshots ### Frame Selection  This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection. ### Diagram Extraction  This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save. ## Links - repo: https://github.com/limina1/video_article_converter - Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE ## Output And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101 Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
@ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content. ## Key Features: ### Video Processing: - Automatically downloads YouTube videos, transcripts, and chapter information - Splits transcripts into sections based on video chapters ### Content Summarization: - Utilizes language models to transform spoken content into clear, readable text - Formats output in AsciiDoc for improved readability and navigation - Highlights key terms and concepts with [[term]] notation for potential cross-referencing ### Diagram Extraction: - Analyzes video entropy to identify static diagram/slide sections - Provides a user-friendly GUI for manual selection of relevant time ranges - Allows users to pick representative frames from selected ranges ## Going Forward: Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care. While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs. ## Screenshots ### Frame Selection  This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection. ### Diagram Extraction  This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save. ## Links - repo: https://github.com/limina1/video_article_converter - Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE ## Output And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101 Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3 @ 9673b322:1b75ee9e
2025-02-13 14:10:06This is some test content Adding a Sample Image 
@ 9673b322:1b75ee9e
2025-02-13 14:10:06This is some test content Adding a Sample Image  @ 2e8970de:63345c7a
2025-02-13 13:39:35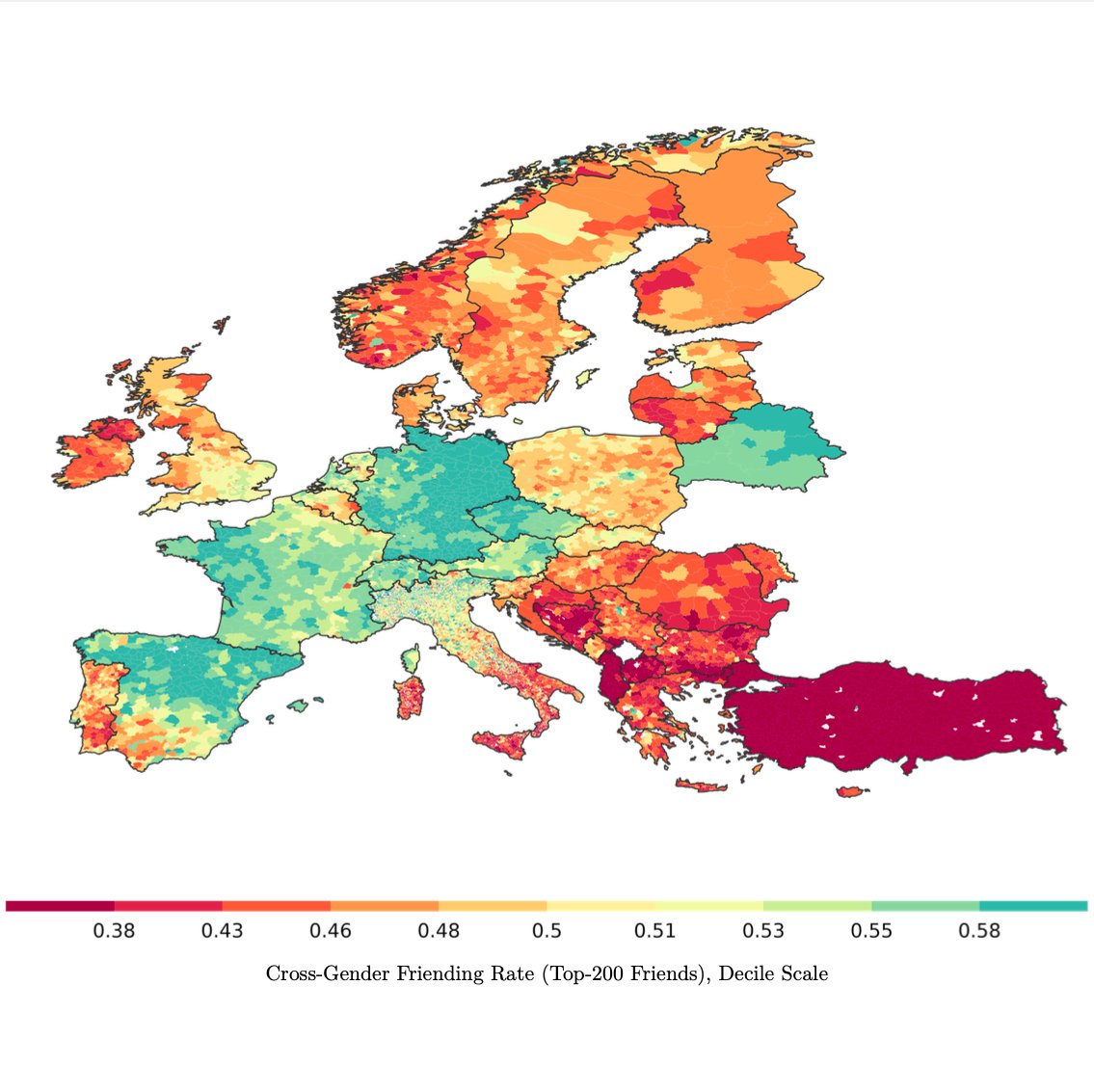 > We measure gender differences using the Cross-Gender Friending Ratio, the ratio of female friends in men's networks to the share of female friends in women's networks in a given place. Men almost always have a lower share of female friends than women do, but the degree varies: 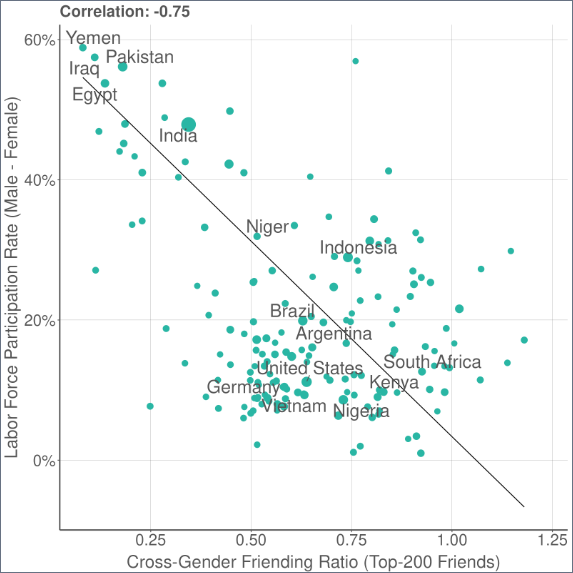 > Across countries, the CGFR is strongly predictive of gender differences in labor force participation. Within countries, we also find a strong correlation with gender attitudes in the World Values Survey, such as beliefs about women's suitability for politics. https://x.com/drew_m_johnston/status/1889794718004826288 originally posted at https://stacker.news/items/884660
@ 2e8970de:63345c7a
2025-02-13 13:39:35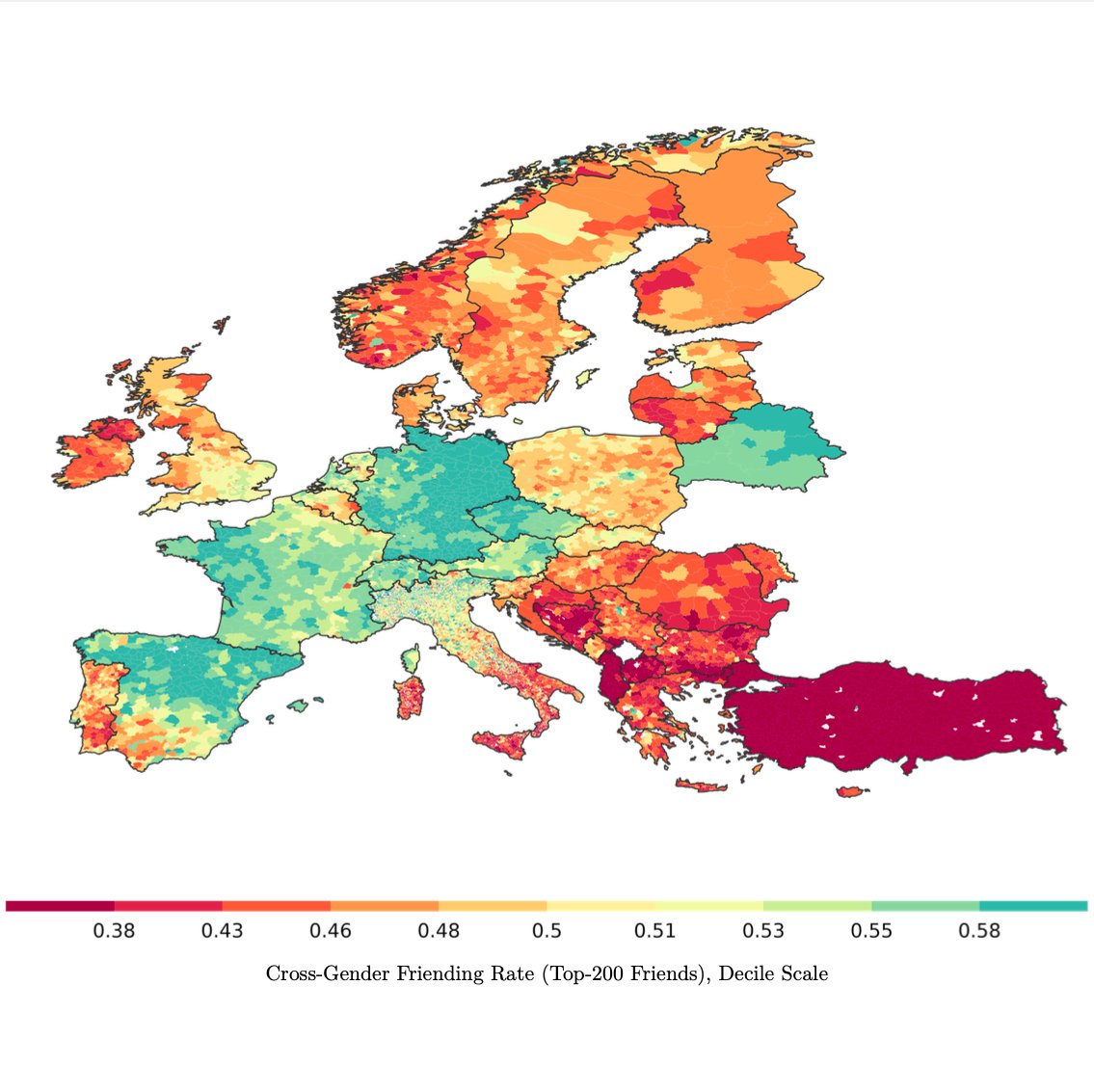 > We measure gender differences using the Cross-Gender Friending Ratio, the ratio of female friends in men's networks to the share of female friends in women's networks in a given place. Men almost always have a lower share of female friends than women do, but the degree varies: 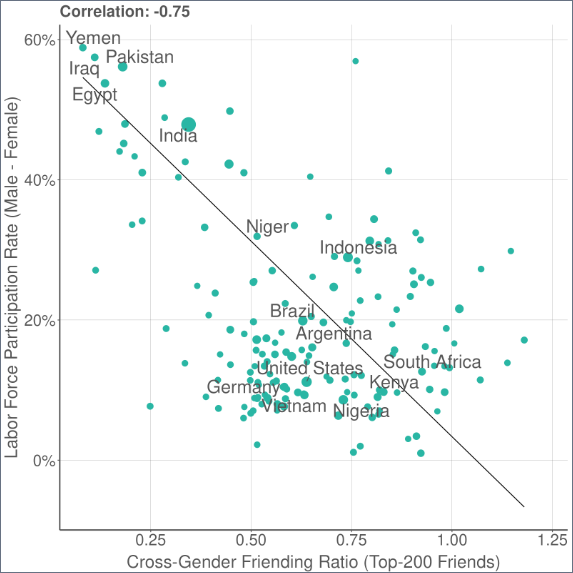 > Across countries, the CGFR is strongly predictive of gender differences in labor force participation. Within countries, we also find a strong correlation with gender attitudes in the World Values Survey, such as beliefs about women's suitability for politics. https://x.com/drew_m_johnston/status/1889794718004826288 originally posted at https://stacker.news/items/884660 @ 32e18276:5c68e245
2025-02-08 20:20:46This period of the Damus OpenSats grant has been productive, and encompasses the work past our alpha release of Notedeck. Since we sent our last report on Dec 5, this encompasses all the work after then. Damus is supported by the OpenSats LTS grant, which allows us to continue working on the goodies below. Thank you! ## Damus Notedeck ### Added - Initial algo timelines (William Casarin) [#712](https://github.com/damus-io/notedeck/pull/712) - Initial support for local-network P2P nostr: multicast support (William Casarin) [#626](https://github.com/damus-io/notedeck/pull/626) - First steps toward the notedeck browser: multiple app support [#565](https://github.com/damus-io/notedeck/pull/565) - Clicking a mention now opens profile page (William Casarin) [5a241d730](https://github.com/damus-io/notedeck/commit/5a241d730e3d83f8057e211485edfde2f3c96e54) - Note previews when hovering reply descriptions (William Casarin) [#591](https://github.com/damus-io/notedeck/pull/591) - Various Android updates and compatibility improvements (Ken Sedgwick, William Casarin) - Media uploads (kernelkind) [#662](https://github.com/damus-io/notedeck/pull/662) - Profile editing (kernelkind) [#625](https://github.com/damus-io/notedeck/pull/625) - Add hashtags to posts (Daniel Saxton) [#592](https://github.com/damus-io/notedeck/pull/592) - Enhanced command-line interface for user interactions (Ken Sedgwick) - Debug features for user relay-list and mute list synchronization (Ken Sedgwick) ### Changed - Major timeline cache refactor (William Casarin) [#653](https://github.com/damus-io/notedeck/pull/653) - Increased ping intervals for network performance (William Casarin) - Migrated to egui v0.29.1 (William Casarin) [#551](https://github.com/damus-io/notedeck/pull/551) - Switch to only notes & replies on some tabs (William Casarin) [#598](https://github.com/damus-io/notedeck/pull/598) - Only show column delete button when not navigating (William Casarin) - Pointer interactions enhancements in UI (William Casarin) - Show profile pictures in column headers (William Casarin) - Show usernames in user columns (William Casarin) - Add confirmation when deleting columns (kernelkind) - Enhance Android build and performance (Ken Sedgwick) - Image cache handling using sha256 hash (kieran) - Introduction of decks_cache and improvements (kernelkind) - Nostrdb update for async support (Ken Sedgwick) - Persistent theme setup across sessions (kernelkind) - Tombstone muted notes (Ken) ### Fixed - Fix GIT_COMMIT_HASH compilation issue (William Casarin) - Fix avatar alignment in profile previews (William Casarin) - Fix broken quote repost hitbox (William Casarin) - Fix crash when navigating in debug mode (William Casarin) - Fix long delays when reconnecting (William Casarin) - Fix repost button size (William Casarin) - Fixed since kind filters (kernelkind) - Clippy warnings resolved (Dimitris Apostolou) ## Damus iOS Work continued on the iOS side. While I was not directly involved in the work since the last report, I have been directing and managing its development. ### Added - Render Gif and video files while composing posts (Swift Coder) - Purple members who have been active for more than a year now get a special badge (Daniel D’Aquino) - Add profile info text in stretchable banner with follow button (Swift Coder) - Paste Gif image similar to jpeg and png files (Swift Coder) ### Changed - Improved clarity of the mute button to indicate it can be used for blocking a user (Daniel D’Aquino) - Made the microphone access request message more clear to users (Daniel D’Aquino) - Improved UX around the label for searching words (Daniel D’Aquino) - Improved accessibility support on some elements (Daniel D’Aquino) ### Fixed - Fixed issue where the "next" button would appear hidden and hard to click on the create account view (Daniel D’Aquino) - Fix non scrollable wallet screen (Swift Coder) - Fixed suggested users category titles to be localizable (Terry Yiu) - Fixed GradientFollowButton to have consistent width and autoscale text limited to 1 line (Terry Yiu) - Fixed right-to-left localization issues (Terry Yiu) - Fixed AddMuteItemView to trim leading and trailing whitespaces from mute text and disallow adding text with only whitespaces (Terry Yiu) - Fixed SideMenuView text to autoscale and limit to 1 line (Terry Yiu) - Fixed an issue where a profile would need to be input twice in the search to be found (Daniel D’Aquino) - Fixed non-breaking spaces in localized strings (Terry Yiu) - Fixed localization issue on Add mute item button (Terry Yiu) - Replace non-breaking spaces with regular spaces as Apple's NSLocalizedString macro does not seem to work with it (Terry Yiu) - Fixed localization issues in RelayConfigView (Terry Yiu) - Fix duplicate uploads (Swift Coder) - Remove duplicate pubkey from Follow Suggestion list (Swift Coder) - Fix Page control indicator (Swift Coder) - Fix damus sharing issues (Swift Coder) - Fixed issue where banner edit button is unclickable (Daniel D’Aquino) - Handle empty notification pages by displaying suitable text (Swift Coder) ## Nostrdb nostrdb, the engine that powers [notecrumbs](https://github.com/damus-io/notecrumbs), damus iOS, and notedeck, continued to improve: ### Added - Added nip50 fulltext searching (William Casarin) [#68](https://github.com/damus-io/nostrdb/pull/68), [demo](nostr:nevent1qqsp3rx83t5h0vdhu4txru76uycfnaegfj3wg6wncamkarcnrccssvcpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqvhpsfmr23gwhv795lgjc8uw0v44z3pe4sg2vlh08k0an3wx3cj9efqkkv) - Added async migrations (William Casarin) [#59](https://github.com/damus-io/nostrdb/pull/59) - Implement author queries (William Casarin) [#57](https://github.com/damus-io/nostrdb/pull/57) - Make `ndb` threadsafe (William Casarin) [#56](https://github.com/damus-io/nostrdb/pull/56) ## Nostrdb Rust Our nostrdb rust bindings also had improvements - Async! Adding efficient, poll-based stream support (William Casarin): [#25](https://github.com/damus-io/nostrdb-rs/pull/25) ## Notecrumbs Notecrumbs, the njump-style opengraph server that powers the damus.io links, got an update that upgraded it to async nostrdb - Switch to async nostrdb-rs (William Casarin) [#16](https://github.com/damus-io/notecrumbs/pull/16) ## How money was used - relay.damus.io server costs - Living expenses ## Next quarter Our goal for next update: zaps, android version, lists, outbox model for notedeck. Olas images in damus iOS, continue switching Damus iOS over to local relay model so we can add outbox support.
@ 32e18276:5c68e245
2025-02-08 20:20:46This period of the Damus OpenSats grant has been productive, and encompasses the work past our alpha release of Notedeck. Since we sent our last report on Dec 5, this encompasses all the work after then. Damus is supported by the OpenSats LTS grant, which allows us to continue working on the goodies below. Thank you! ## Damus Notedeck ### Added - Initial algo timelines (William Casarin) [#712](https://github.com/damus-io/notedeck/pull/712) - Initial support for local-network P2P nostr: multicast support (William Casarin) [#626](https://github.com/damus-io/notedeck/pull/626) - First steps toward the notedeck browser: multiple app support [#565](https://github.com/damus-io/notedeck/pull/565) - Clicking a mention now opens profile page (William Casarin) [5a241d730](https://github.com/damus-io/notedeck/commit/5a241d730e3d83f8057e211485edfde2f3c96e54) - Note previews when hovering reply descriptions (William Casarin) [#591](https://github.com/damus-io/notedeck/pull/591) - Various Android updates and compatibility improvements (Ken Sedgwick, William Casarin) - Media uploads (kernelkind) [#662](https://github.com/damus-io/notedeck/pull/662) - Profile editing (kernelkind) [#625](https://github.com/damus-io/notedeck/pull/625) - Add hashtags to posts (Daniel Saxton) [#592](https://github.com/damus-io/notedeck/pull/592) - Enhanced command-line interface for user interactions (Ken Sedgwick) - Debug features for user relay-list and mute list synchronization (Ken Sedgwick) ### Changed - Major timeline cache refactor (William Casarin) [#653](https://github.com/damus-io/notedeck/pull/653) - Increased ping intervals for network performance (William Casarin) - Migrated to egui v0.29.1 (William Casarin) [#551](https://github.com/damus-io/notedeck/pull/551) - Switch to only notes & replies on some tabs (William Casarin) [#598](https://github.com/damus-io/notedeck/pull/598) - Only show column delete button when not navigating (William Casarin) - Pointer interactions enhancements in UI (William Casarin) - Show profile pictures in column headers (William Casarin) - Show usernames in user columns (William Casarin) - Add confirmation when deleting columns (kernelkind) - Enhance Android build and performance (Ken Sedgwick) - Image cache handling using sha256 hash (kieran) - Introduction of decks_cache and improvements (kernelkind) - Nostrdb update for async support (Ken Sedgwick) - Persistent theme setup across sessions (kernelkind) - Tombstone muted notes (Ken) ### Fixed - Fix GIT_COMMIT_HASH compilation issue (William Casarin) - Fix avatar alignment in profile previews (William Casarin) - Fix broken quote repost hitbox (William Casarin) - Fix crash when navigating in debug mode (William Casarin) - Fix long delays when reconnecting (William Casarin) - Fix repost button size (William Casarin) - Fixed since kind filters (kernelkind) - Clippy warnings resolved (Dimitris Apostolou) ## Damus iOS Work continued on the iOS side. While I was not directly involved in the work since the last report, I have been directing and managing its development. ### Added - Render Gif and video files while composing posts (Swift Coder) - Purple members who have been active for more than a year now get a special badge (Daniel D’Aquino) - Add profile info text in stretchable banner with follow button (Swift Coder) - Paste Gif image similar to jpeg and png files (Swift Coder) ### Changed - Improved clarity of the mute button to indicate it can be used for blocking a user (Daniel D’Aquino) - Made the microphone access request message more clear to users (Daniel D’Aquino) - Improved UX around the label for searching words (Daniel D’Aquino) - Improved accessibility support on some elements (Daniel D’Aquino) ### Fixed - Fixed issue where the "next" button would appear hidden and hard to click on the create account view (Daniel D’Aquino) - Fix non scrollable wallet screen (Swift Coder) - Fixed suggested users category titles to be localizable (Terry Yiu) - Fixed GradientFollowButton to have consistent width and autoscale text limited to 1 line (Terry Yiu) - Fixed right-to-left localization issues (Terry Yiu) - Fixed AddMuteItemView to trim leading and trailing whitespaces from mute text and disallow adding text with only whitespaces (Terry Yiu) - Fixed SideMenuView text to autoscale and limit to 1 line (Terry Yiu) - Fixed an issue where a profile would need to be input twice in the search to be found (Daniel D’Aquino) - Fixed non-breaking spaces in localized strings (Terry Yiu) - Fixed localization issue on Add mute item button (Terry Yiu) - Replace non-breaking spaces with regular spaces as Apple's NSLocalizedString macro does not seem to work with it (Terry Yiu) - Fixed localization issues in RelayConfigView (Terry Yiu) - Fix duplicate uploads (Swift Coder) - Remove duplicate pubkey from Follow Suggestion list (Swift Coder) - Fix Page control indicator (Swift Coder) - Fix damus sharing issues (Swift Coder) - Fixed issue where banner edit button is unclickable (Daniel D’Aquino) - Handle empty notification pages by displaying suitable text (Swift Coder) ## Nostrdb nostrdb, the engine that powers [notecrumbs](https://github.com/damus-io/notecrumbs), damus iOS, and notedeck, continued to improve: ### Added - Added nip50 fulltext searching (William Casarin) [#68](https://github.com/damus-io/nostrdb/pull/68), [demo](nostr:nevent1qqsp3rx83t5h0vdhu4txru76uycfnaegfj3wg6wncamkarcnrccssvcpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqvhpsfmr23gwhv795lgjc8uw0v44z3pe4sg2vlh08k0an3wx3cj9efqkkv) - Added async migrations (William Casarin) [#59](https://github.com/damus-io/nostrdb/pull/59) - Implement author queries (William Casarin) [#57](https://github.com/damus-io/nostrdb/pull/57) - Make `ndb` threadsafe (William Casarin) [#56](https://github.com/damus-io/nostrdb/pull/56) ## Nostrdb Rust Our nostrdb rust bindings also had improvements - Async! Adding efficient, poll-based stream support (William Casarin): [#25](https://github.com/damus-io/nostrdb-rs/pull/25) ## Notecrumbs Notecrumbs, the njump-style opengraph server that powers the damus.io links, got an update that upgraded it to async nostrdb - Switch to async nostrdb-rs (William Casarin) [#16](https://github.com/damus-io/notecrumbs/pull/16) ## How money was used - relay.damus.io server costs - Living expenses ## Next quarter Our goal for next update: zaps, android version, lists, outbox model for notedeck. Olas images in damus iOS, continue switching Damus iOS over to local relay model so we can add outbox support. @ c2827524:5f45b2f7
2025-02-13 11:54:16> innèsto s. m. [der. di innestare]. – 1. In agraria: a. Operazione con cui si fa concrescere sopra una pianta (detta portainnesto o soggetto) una parte di un altro della stessa specie o di specie differenti (detto nesto o oggetto), **al fine di formare un nuovo individuo più pregiato o più produttivo o più giovane**: fare, operare, praticare un innesto. Le collaborazioni sono di una potenza micidiale. Quelle che si sviluppano nello spazio #Bitcoin ancora di più. Non è più una collaborazione, è un #innesto: rami di alberi diversi, destinati da soli a dare grandi frutti, si fondono per **donare ad un intero ecosistema sapori ancora più deliziosi**. Contributi e suggerimenti vanno e vengono alla velocità della luce, col sorriso, senza sacrificio e sempre con la volontà di migliorarsi e crescere. Lo spazio #Bitcoin è una fabbrica magica, che accoglie minuscoli semini(*) da chiunque voglia partecipare, volontariamente, alla crescita della cultura Bitcoin. Ma li trasforma in un **incanto**. In solitaria i semini sarebbero destinati comunque a grandi cose e questo è già, di per sé, meraviglioso. La fabbrica magica, invece, li fa germogliare, fiorire e fruttare in maniera ancora più potente. Quando la magia è totale, avviene l’*innesto*, **la generazione di una nuova creatura più pregiata**. Sta succedendo davanti ai miei occhi. Sono onorata di poter assistere a questo mini miracolo della vita e, manco a dirlo, felice di farne parte. Non è solo cambiare atteggiamento, smussare frizioni e rigidità o correggere la propria visione, è proprio ampliare sé stessi accogliendo gli altri. Grazie nostr:npub1uhj92lnwh8rrhhuvulfqstk4g0ayx0zx35wj2d62jueqheknkxks5m4zj6 nostr:npub1au23c73cpaq2whtazjf6cdrmvam6nkd4lg928nwmgl78374kn29sq9t53j nostr:npub1awnu9vg352863e7tqlc6urlw7jgdf8vf00tmr76uuhflp4nnn68sjmnnl3 e nostr:npub1lrurmgmlfl4u72258fc4q5ke7tr82kw5xct5vchdmzr9uhmx6j4qn3t72a (1) Semini, non #seed [non chiamatelo seed, si dice mnemonica (cit.)] Siccome in italiano la parola **seme** porta alla mente anche *giochini di parole fiat*, se siete qui per perculare fate pure. -> H.F.S.P. 🤣
@ c2827524:5f45b2f7
2025-02-13 11:54:16> innèsto s. m. [der. di innestare]. – 1. In agraria: a. Operazione con cui si fa concrescere sopra una pianta (detta portainnesto o soggetto) una parte di un altro della stessa specie o di specie differenti (detto nesto o oggetto), **al fine di formare un nuovo individuo più pregiato o più produttivo o più giovane**: fare, operare, praticare un innesto. Le collaborazioni sono di una potenza micidiale. Quelle che si sviluppano nello spazio #Bitcoin ancora di più. Non è più una collaborazione, è un #innesto: rami di alberi diversi, destinati da soli a dare grandi frutti, si fondono per **donare ad un intero ecosistema sapori ancora più deliziosi**. Contributi e suggerimenti vanno e vengono alla velocità della luce, col sorriso, senza sacrificio e sempre con la volontà di migliorarsi e crescere. Lo spazio #Bitcoin è una fabbrica magica, che accoglie minuscoli semini(*) da chiunque voglia partecipare, volontariamente, alla crescita della cultura Bitcoin. Ma li trasforma in un **incanto**. In solitaria i semini sarebbero destinati comunque a grandi cose e questo è già, di per sé, meraviglioso. La fabbrica magica, invece, li fa germogliare, fiorire e fruttare in maniera ancora più potente. Quando la magia è totale, avviene l’*innesto*, **la generazione di una nuova creatura più pregiata**. Sta succedendo davanti ai miei occhi. Sono onorata di poter assistere a questo mini miracolo della vita e, manco a dirlo, felice di farne parte. Non è solo cambiare atteggiamento, smussare frizioni e rigidità o correggere la propria visione, è proprio ampliare sé stessi accogliendo gli altri. Grazie nostr:npub1uhj92lnwh8rrhhuvulfqstk4g0ayx0zx35wj2d62jueqheknkxks5m4zj6 nostr:npub1au23c73cpaq2whtazjf6cdrmvam6nkd4lg928nwmgl78374kn29sq9t53j nostr:npub1awnu9vg352863e7tqlc6urlw7jgdf8vf00tmr76uuhflp4nnn68sjmnnl3 e nostr:npub1lrurmgmlfl4u72258fc4q5ke7tr82kw5xct5vchdmzr9uhmx6j4qn3t72a (1) Semini, non #seed [non chiamatelo seed, si dice mnemonica (cit.)] Siccome in italiano la parola **seme** porta alla mente anche *giochini di parole fiat*, se siete qui per perculare fate pure. -> H.F.S.P. 🤣 @ e5de231a:958477f6
2025-02-13 11:32:41Market Insights: Advanced Semiconductor Packaging Market Size was valued at USD 37.90 Billion in 2024. The Advanced Semiconductor Packaging Market industry is projected to grow from USD 40.94 Billion in 2025 to USD 81.85 Billion by 2034, exhibiting a compound annual growth rate (CAGR) of 8.0% during the forecast period (2025 - 2034). The integration of semiconductor components in vehicles will fuel the global semiconductor advanced packaging market growth. The electrification of automobiles as well as the rising demand for automation in vehicles are expected to be a significant market driver for the Advanced Semiconductor Packaging Market. In the dynamic landscape of technological advancements, the semiconductor industry stands at the forefront, steering innovation and progress. The [Advanced Semiconductor Packaging Market](https://www.marketresearchfuture.com/reports/advanced-semiconductor-packaging-market-12505), a crucial facet of this realm, plays a pivotal role in shaping the future of electronic devices. In this comprehensive exploration, we delve into the intricacies of this market, unraveling its complexities and forecasting its trajectory. Understanding the Essence of Advanced Semiconductor Packaging What Sets Advanced Semiconductor Packaging Apart? Semiconductor packaging is the art and science of protecting and enhancing semiconductor devices, ensuring optimal performance in electronic applications. As technology evolves, the demand for more efficient, compact, and powerful semiconductor packaging solutions has surged. This is where the 'advanced' in Advanced Semiconductor Packaging becomes a game-changer. Miniaturization and Integration: The driving force behind advanced packaging lies in the quest for smaller, yet more potent, electronic components. The market is witnessing a paradigm shift towards compact designs without compromising on functionality. Heterogeneous Integration: Combining diverse materials and technologies into a single package is the hallmark of advanced semiconductor packaging. This amalgamation fosters improved performance, energy efficiency, and overall system reliability. Enhanced Thermal Management: As electronic devices become more powerful, managing heat dissipation becomes a critical challenge. Advanced packaging solutions incorporate innovative thermal management techniques to ensure sustained high performance. Market Trends and Projections Riding the Waves of Innovation 5G Integration: The advent of 5G technology has propelled the need for advanced semiconductor packaging to new heights. The market is witnessing a surge in demand for packaging solutions that can support the high-frequency requirements of 5G-enabled devices. Artificial Intelligence (AI) Integration: AI-driven applications demand robust semiconductor solutions. Advanced packaging, with its focus on efficient power delivery and heat dissipation, aligns perfectly with the requirements of AI-powered devices. Automotive Electronics: The automotive industry's shift towards electric and autonomous vehicles has fueled the demand for advanced semiconductor packaging. These packages need to withstand harsh environments while delivering exceptional performance. Market Dynamics and Key Players The Advanced Semiconductor Packaging Market is characterized by intense competition and rapid technological advancements. Key players in this landscape include: Intel Corporation: A pioneer in semiconductor technology, Intel continues to lead the market with innovations in packaging solutions. Advanced Micro Devices (AMD): Renowned for its cutting-edge processors, AMD's foray into advanced packaging has added a new dimension to the market. Taiwan Semiconductor Manufacturing Company (TSMC): As a global semiconductor manufacturing giant, TSMC's influence on the market is undeniable, shaping the industry's future through advanced packaging technologies. Challenges and Future Prospects Navigating the Road Ahead While the Advanced Semiconductor Packaging Market is poised for growth, it is not without its challenges: Complexity of Integration: As technologies converge, integrating diverse components into a single package poses significant technical challenges. Supply Chain Disruptions: The global semiconductor shortage has underscored the vulnerability of the supply chain. Addressing these disruptions is crucial for sustained market growth. Environmental Considerations: The semiconductor industry is under increasing scrutiny for its environmental impact. Sustainable packaging solutions and responsible manufacturing practices are becoming paramount. Related Reports: [Super Capacitors Energy Storage System Market](https://www.marketresearchfuture.com/reports/super-capacitors-battery-energy-storage-system-market-1158) [Interactive Whiteboard Market](https://www.marketresearchfuture.com/reports/interactive-whiteboard-market-6087) Conclusion In conclusion, the Advanced Semiconductor Packaging Market is a dynamic arena where innovation converges with necessity. As we navigate the complexities of an interconnected world, the role of advanced packaging in shaping the future of electronics cannot be overstated. The market's trajectory is marked by challenges, but also by unprecedented opportunities for those at the forefront of technological evolution.
@ e5de231a:958477f6
2025-02-13 11:32:41Market Insights: Advanced Semiconductor Packaging Market Size was valued at USD 37.90 Billion in 2024. The Advanced Semiconductor Packaging Market industry is projected to grow from USD 40.94 Billion in 2025 to USD 81.85 Billion by 2034, exhibiting a compound annual growth rate (CAGR) of 8.0% during the forecast period (2025 - 2034). The integration of semiconductor components in vehicles will fuel the global semiconductor advanced packaging market growth. The electrification of automobiles as well as the rising demand for automation in vehicles are expected to be a significant market driver for the Advanced Semiconductor Packaging Market. In the dynamic landscape of technological advancements, the semiconductor industry stands at the forefront, steering innovation and progress. The [Advanced Semiconductor Packaging Market](https://www.marketresearchfuture.com/reports/advanced-semiconductor-packaging-market-12505), a crucial facet of this realm, plays a pivotal role in shaping the future of electronic devices. In this comprehensive exploration, we delve into the intricacies of this market, unraveling its complexities and forecasting its trajectory. Understanding the Essence of Advanced Semiconductor Packaging What Sets Advanced Semiconductor Packaging Apart? Semiconductor packaging is the art and science of protecting and enhancing semiconductor devices, ensuring optimal performance in electronic applications. As technology evolves, the demand for more efficient, compact, and powerful semiconductor packaging solutions has surged. This is where the 'advanced' in Advanced Semiconductor Packaging becomes a game-changer. Miniaturization and Integration: The driving force behind advanced packaging lies in the quest for smaller, yet more potent, electronic components. The market is witnessing a paradigm shift towards compact designs without compromising on functionality. Heterogeneous Integration: Combining diverse materials and technologies into a single package is the hallmark of advanced semiconductor packaging. This amalgamation fosters improved performance, energy efficiency, and overall system reliability. Enhanced Thermal Management: As electronic devices become more powerful, managing heat dissipation becomes a critical challenge. Advanced packaging solutions incorporate innovative thermal management techniques to ensure sustained high performance. Market Trends and Projections Riding the Waves of Innovation 5G Integration: The advent of 5G technology has propelled the need for advanced semiconductor packaging to new heights. The market is witnessing a surge in demand for packaging solutions that can support the high-frequency requirements of 5G-enabled devices. Artificial Intelligence (AI) Integration: AI-driven applications demand robust semiconductor solutions. Advanced packaging, with its focus on efficient power delivery and heat dissipation, aligns perfectly with the requirements of AI-powered devices. Automotive Electronics: The automotive industry's shift towards electric and autonomous vehicles has fueled the demand for advanced semiconductor packaging. These packages need to withstand harsh environments while delivering exceptional performance. Market Dynamics and Key Players The Advanced Semiconductor Packaging Market is characterized by intense competition and rapid technological advancements. Key players in this landscape include: Intel Corporation: A pioneer in semiconductor technology, Intel continues to lead the market with innovations in packaging solutions. Advanced Micro Devices (AMD): Renowned for its cutting-edge processors, AMD's foray into advanced packaging has added a new dimension to the market. Taiwan Semiconductor Manufacturing Company (TSMC): As a global semiconductor manufacturing giant, TSMC's influence on the market is undeniable, shaping the industry's future through advanced packaging technologies. Challenges and Future Prospects Navigating the Road Ahead While the Advanced Semiconductor Packaging Market is poised for growth, it is not without its challenges: Complexity of Integration: As technologies converge, integrating diverse components into a single package poses significant technical challenges. Supply Chain Disruptions: The global semiconductor shortage has underscored the vulnerability of the supply chain. Addressing these disruptions is crucial for sustained market growth. Environmental Considerations: The semiconductor industry is under increasing scrutiny for its environmental impact. Sustainable packaging solutions and responsible manufacturing practices are becoming paramount. Related Reports: [Super Capacitors Energy Storage System Market](https://www.marketresearchfuture.com/reports/super-capacitors-battery-energy-storage-system-market-1158) [Interactive Whiteboard Market](https://www.marketresearchfuture.com/reports/interactive-whiteboard-market-6087) Conclusion In conclusion, the Advanced Semiconductor Packaging Market is a dynamic arena where innovation converges with necessity. As we navigate the complexities of an interconnected world, the role of advanced packaging in shaping the future of electronics cannot be overstated. The market's trajectory is marked by challenges, but also by unprecedented opportunities for those at the forefront of technological evolution. @ d57360cb:4fe7d935
2025-02-06 18:31:30Mindfulness often has the misconception that by practicing you can stop your mind from thinking and obtain an empty mind. While one can definitely achieve moments of emptiness in thinking, this view that emptiness is the goal can be the very obstacle in your way leading to frustration with the practice. If we adjust our perspective and see mindfulness as learning to accept the situations we find ourselves in and adjust to them rather than fighting them, we achieve a kind of grace under pressure. The thoughts are part of the practice, just like cars on the road are part of driving, or the danger of a punch is always a threat to a boxer. The difference between the novice and the seasoned is one has accepted and acclimated to the realities of the situation instead of fighting them, in this one finds freedom.
@ d57360cb:4fe7d935
2025-02-06 18:31:30Mindfulness often has the misconception that by practicing you can stop your mind from thinking and obtain an empty mind. While one can definitely achieve moments of emptiness in thinking, this view that emptiness is the goal can be the very obstacle in your way leading to frustration with the practice. If we adjust our perspective and see mindfulness as learning to accept the situations we find ourselves in and adjust to them rather than fighting them, we achieve a kind of grace under pressure. The thoughts are part of the practice, just like cars on the road are part of driving, or the danger of a punch is always a threat to a boxer. The difference between the novice and the seasoned is one has accepted and acclimated to the realities of the situation instead of fighting them, in this one finds freedom. @ d360efec:14907b5f
2025-02-13 11:15:12**Top-Down Analysis:** กลยุทธ์การเทรดเพื่อมองภาพรวมและจับจังหวะทำกำไร ในโลกของการเทรดที่เต็มไปด้วยความผันผวน การมีเครื่องมือวิเคราะห์ที่แข็งแกร่งเป็นสิ่งสำคัญอย่างยิ่งที่จะช่วยนำทางให้เทรดเดอร์สามารถตัดสินใจได้อย่างมีหลักการและเพิ่มโอกาสในการทำกำไร หนึ่งในเครื่องมือที่ได้รับความนิยมและมีประสิทธิภาพคือ "Top-Down Analysis" หรือการวิเคราะห์จากบนลงล่าง ซึ่งเป็นวิธีการมองภาพรวมของตลาดก่อนที่จะเจาะจงไปที่สินทรัพย์ที่เราสนใจ บทความนี้จะพาคุณไปทำความเข้าใจกับ Top-Down Analysis อย่างละเอียด พร้อมทั้งแนะนำกลยุทธ์การเทรดที่สามารถนำไปปรับใช้ได้จริง **Top-Down Analysis คืออะไร?** Top-Down Analysis เป็นกระบวนการวิเคราะห์ตลาดที่เริ่มต้นจากการพิจารณาภาพรวมในกรอบเวลาที่ใหญ่ขึ้น ก่อนที่จะค่อยๆ ย่อยลงไปในกรอบเวลาที่เล็กลง เพื่อทำความเข้าใจบริบทของตลาดและหาจังหวะการเทรดที่เหมาะสม วิธีการนี้ช่วยให้เทรดเดอร์สามารถมองเห็นทิศทางหลักของตลาด, แนวโน้มที่กำลังเกิดขึ้น, ระดับราคาสำคัญ, และความสมดุลระหว่างอุปสงค์และอุปทาน ก่อนที่จะตัดสินใจเข้าเทรดในกรอบเวลาที่เล็กลง **องค์ประกอบสำคัญของ Top-Down Analysis (อ้างอิงจากภาพ)** ภาพ "Top-Down Analysis" ได้สรุปองค์ประกอบสำคัญของการวิเคราะห์นี้ไว้อย่างชัดเจน โดยแบ่งการวิเคราะห์ออกเป็น 3 กรอบเวลาหลัก: 4 ชั่วโมง (4H), 1 ชั่วโมง (1H), และ 15 นาที (15min) แต่ละกรอบเวลามีองค์ประกอบที่ต้องพิจารณาดังนี้: 1. กรอบเวลา 4 ชั่วโมง (4H): ภาพรวมตลาดและทิศทางหลัก ในกรอบเวลา 4 ชั่วโมง เราจะเน้นการวิเคราะห์ภาพรวมของตลาด เพื่อกำหนดทิศทางหลักและแนวโน้มในระยะกลาง องค์ประกอบสำคัญในกรอบเวลานี้คือ: * Direction (ทิศทาง): ประเมินทิศทางที่ตลาดกำลังเคลื่อนที่ไป โดยพิจารณาจากแนวโน้มและโครงสร้างราคาในภาพรวม ตลาดกำลังเป็นขาขึ้น, ขาลง หรืออยู่ในช่วง Sideways? * Trend (แนวโน้ม): ระบุแนวโน้มหลักของตลาด ไม่ว่าจะเป็นแนวโน้มขาขึ้น (Uptrend), แนวโน้มขาลง (Downtrend) หรือ Sideways การเข้าใจแนวโน้มช่วยในการกำหนดกลยุทธ์การเทรดที่เหมาะสม * Key levels (ระดับราคาสำคัญ): หาระดับราคาแนวรับและแนวต้านที่สำคัญในกรอบเวลา 4 ชั่วโมง ระดับเหล่านี้มักเป็นจุดที่ราคาเคยมีการกลับตัวหรือพักตัวในอดีต และอาจเป็นบริเวณที่ราคาจะตอบสนองอีกครั้งในอนาคต * Supply & Demand (อุปทานและอุปสงค์): วิเคราะห์ความสมดุลระหว่างแรงซื้อ (Demand) และแรงขาย (Supply) ในตลาด โดยพิจารณาจากพฤติกรรมราคาบริเวณแนวรับแนวต้าน และสัญญาณจากเครื่องมือวิเคราะห์อื่นๆ (ถ้าใช้) 2. กรอบเวลา 1 ชั่วโมง (1H): หาจังหวะและบริเวณที่น่าสนใจ เมื่อได้ภาพรวมและทิศทางหลักจากกรอบ 4H แล้ว เราจะย่อยลงมาในกรอบ 1 ชั่วโมง เพื่อหาจังหวะการเทรดที่สอดคล้องกับทิศทางหลัก และมองหารูปแบบราคาที่น่าสนใจ องค์ประกอบสำคัญในกรอบเวลานี้คือ: * Breaks (การทะลุ): สังเกตการทะลุแนวรับแนวต้าน หรือระดับราคาสำคัญในกรอบ 1H ที่สอดคล้องกับทิศทางหลักใน 4H การทะลุเหล่านี้อาจเป็นสัญญาณของการเคลื่อนไหวครั้งใหญ่ของราคา * Reversals (การกลับตัว): มองหารูปแบบการกลับตัวของราคาที่อาจเกิดขึ้นบริเวณระดับราคาสำคัญในกรอบ 1H ซึ่งบ่งบอกถึงจุดสิ้นสุดของแนวโน้มปัจจุบันและเริ่มต้นแนวโน้มใหม่ * OB (Order Blocks): ระบุบริเวณ Order Blocks ในกรอบ 1H ซึ่งเป็นพื้นที่ที่มีการสั่งซื้อขายจำนวนมากในอดีต Order Blocks เหล่านี้มักจะทำหน้าที่เป็นแนวรับแนวต้านในอนาคต * FVG (Fair Value Gaps): มองหา Fair Value Gaps ในกรอบ 1H ซึ่งเป็นช่องว่างของราคาที่เกิดจากการเคลื่อนไหวอย่างรวดเร็ว FVG มักจะเป็นเป้าหมายของราคาในอนาคต เนื่องจากราคาอาจจะกลับมาปิดช่องว่างเหล่านี้ * Liquidity (สภาพคล่อง): ประเมินสภาพคล่องบริเวณระดับราคาที่เราสนใจในกรอบ 1H บริเวณที่มีสภาพคล่องสูงมักจะดึงดูดนักลงทุนรายใหญ่ และอาจทำให้เกิดการเคลื่อนไหวของราคาที่รุนแรง 3. กรอบเวลา 15 นาที (15min): ยืนยันสัญญาณและหาจุดเข้าเทรด ในกรอบเวลา 15 นาที เราจะเน้นการยืนยันสัญญาณการเทรด และหาจุดเข้าเทรดที่แม่นยำ เพื่อลดความเสี่ยงในการเข้าเทรดเร็วเกินไป องค์ประกอบสำคัญในกรอบเวลานี้คือ: * Confirmation (การยืนยัน): รอสัญญาณยืนยันการเคลื่อนไหวของราคาในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบ 1H และ 4H สัญญาณยืนยันอาจมาในรูปแบบของแท่งเทียนกลับตัว, รูปแบบ Chart Patterns, หรือสัญญาณจาก Indicators * จุดเข้าเทรด: เมื่อมีสัญญาณยืนยันที่ชัดเจนในกรอบ 15 นาที และสอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น จึงตัดสินใจเข้าเทรด โดยกำหนด Stop Loss เพื่อจำกัดความเสี่ยง และ Take Profit เพื่อตั้งเป้าหมายในการทำกำไร **กลยุทธ์การเทรด Top-Down Analysis: ขั้นตอนสู่ความสำเร็จ** เพื่อนำ Top-Down Analysis ไปใช้ในการเทรดอย่างมีประสิทธิภาพ เราสามารถทำตามขั้นตอนต่อไปนี้: 1. **เริ่มต้นที่ 4H**: กำหนดทิศทางและแนวโน้มหลัก วิเคราะห์กราฟ 4H เพื่อระบุทิศทางหลักของตลาด แนวโน้ม และระดับราคาสำคัญ ประเมินความสมดุลของ Supply & Demand เพื่อกำหนด Bias การเทรด (เน้นซื้อหรือขาย) 2. **เจาะลึก 1H:** หาจังหวะและบริเวณที่น่าสนใจ เมื่อได้ทิศทางหลักจาก 4H แล้ว ให้ย่อยลงมาดูกราฟ 1H เพื่อหารูปแบบราคาที่น่าสนใจ เช่น การทะลุแนวรับแนวต้าน, รูปแบบการกลับตัว, Order Blocks, Fair Value Gaps และบริเวณที่มีสภาพคล่องสูง 3. **ยืนยันใน 15min:** หาจุดเข้าเทรดที่แม่นยำ รอสัญญาณยืนยันในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น ใช้ Price Action, แท่งเทียน, หรือ Indicators เพื่อยืนยันสัญญาณ และหาจุดเข้าเทรดที่แม่นยำ พร้อมกำหนด Stop Loss และ Take Profit ที่เหมาะสม **ประโยชน์ของการใช้ Top-Down Analysis** * มองเห็นภาพรวมตลาด: ช่วยให้เทรดเดอร์เข้าใจบริบทของตลาดในภาพรวม ไม่หลงทางในรายละเอียดเล็กๆ น้อยๆ * ตัดสินใจเทรดอย่างมีหลักการ: ทำให้การตัดสินใจเทรดมีเหตุผลและมีข้อมูลสนับสนุนมากขึ้น ไม่ใช่แค่การคาดเดา * เพิ่มความแม่นยำในการเทรด: การวิเคราะห์หลายกรอบเวลาช่วยกรองสัญญาณรบกวน และเพิ่มโอกาสในการเข้าเทรดในทิศทางที่ถูกต้อง * ลดความเสี่ยง: ช่วยลดโอกาสในการเทรดสวนทางแนวโน้มหลักของตลาด และช่วยในการกำหนด Stop Loss ที่เหมาะสม **ข้อควรจำและข้อควรระวัง** * ฝึกฝนและสังเกต: Top-Down Analysis ต้องอาศัยการฝึกฝนและการสังเกตกราฟราคาอย่างสม่ำเสมอ เพื่อพัฒนาความเข้าใจและทักษะในการวิเคราะห์ * ปรับใช้ให้เข้ากับสไตล์: ปรับกลยุทธ์ให้เข้ากับสไตล์การเทรดของคุณ และสินทรัพย์ที่คุณเทรด * บริหารความเสี่ยง: ให้ความสำคัญกับการบริหารความเสี่ยงเสมอ กำหนดขนาด Position ที่เหมาะสม และใช้ Stop Loss ทุกครั้ง * ไม่มีกลยุทธ์ใดสมบูรณ์แบบ: Top-Down Analysis เป็นเครื่องมือที่มีประสิทธิภาพ แต่ไม่มีกลยุทธ์ใดที่รับประกันผลกำไร 100% การเทรดมีความเสี่ยง โปรดศึกษาและทำความเข้าใจความเสี่ยงก่อนตัดสินใจลงทุน **สรุป** Top-Down Analysis เป็นกลยุทธ์การเทรดที่ทรงพลัง ซึ่งช่วยให้เทรดเดอร์สามารถวิเคราะห์ตลาดอย่างเป็นระบบ มองภาพรวม และจับจังหวะการเทรดได้อย่างแม่นยำ การนำหลักการของ Top-Down Analysis ไปปรับใช้ในการเทรด จะช่วยเพิ่มประสิทธิภาพในการตัดสินใจ และเพิ่มโอกาสในการประสบความสำเร็จในตลาดการเงินได้อย่างยั่งยืน
@ d360efec:14907b5f
2025-02-13 11:15:12**Top-Down Analysis:** กลยุทธ์การเทรดเพื่อมองภาพรวมและจับจังหวะทำกำไร ในโลกของการเทรดที่เต็มไปด้วยความผันผวน การมีเครื่องมือวิเคราะห์ที่แข็งแกร่งเป็นสิ่งสำคัญอย่างยิ่งที่จะช่วยนำทางให้เทรดเดอร์สามารถตัดสินใจได้อย่างมีหลักการและเพิ่มโอกาสในการทำกำไร หนึ่งในเครื่องมือที่ได้รับความนิยมและมีประสิทธิภาพคือ "Top-Down Analysis" หรือการวิเคราะห์จากบนลงล่าง ซึ่งเป็นวิธีการมองภาพรวมของตลาดก่อนที่จะเจาะจงไปที่สินทรัพย์ที่เราสนใจ บทความนี้จะพาคุณไปทำความเข้าใจกับ Top-Down Analysis อย่างละเอียด พร้อมทั้งแนะนำกลยุทธ์การเทรดที่สามารถนำไปปรับใช้ได้จริง **Top-Down Analysis คืออะไร?** Top-Down Analysis เป็นกระบวนการวิเคราะห์ตลาดที่เริ่มต้นจากการพิจารณาภาพรวมในกรอบเวลาที่ใหญ่ขึ้น ก่อนที่จะค่อยๆ ย่อยลงไปในกรอบเวลาที่เล็กลง เพื่อทำความเข้าใจบริบทของตลาดและหาจังหวะการเทรดที่เหมาะสม วิธีการนี้ช่วยให้เทรดเดอร์สามารถมองเห็นทิศทางหลักของตลาด, แนวโน้มที่กำลังเกิดขึ้น, ระดับราคาสำคัญ, และความสมดุลระหว่างอุปสงค์และอุปทาน ก่อนที่จะตัดสินใจเข้าเทรดในกรอบเวลาที่เล็กลง **องค์ประกอบสำคัญของ Top-Down Analysis (อ้างอิงจากภาพ)** ภาพ "Top-Down Analysis" ได้สรุปองค์ประกอบสำคัญของการวิเคราะห์นี้ไว้อย่างชัดเจน โดยแบ่งการวิเคราะห์ออกเป็น 3 กรอบเวลาหลัก: 4 ชั่วโมง (4H), 1 ชั่วโมง (1H), และ 15 นาที (15min) แต่ละกรอบเวลามีองค์ประกอบที่ต้องพิจารณาดังนี้: 1. กรอบเวลา 4 ชั่วโมง (4H): ภาพรวมตลาดและทิศทางหลัก ในกรอบเวลา 4 ชั่วโมง เราจะเน้นการวิเคราะห์ภาพรวมของตลาด เพื่อกำหนดทิศทางหลักและแนวโน้มในระยะกลาง องค์ประกอบสำคัญในกรอบเวลานี้คือ: * Direction (ทิศทาง): ประเมินทิศทางที่ตลาดกำลังเคลื่อนที่ไป โดยพิจารณาจากแนวโน้มและโครงสร้างราคาในภาพรวม ตลาดกำลังเป็นขาขึ้น, ขาลง หรืออยู่ในช่วง Sideways? * Trend (แนวโน้ม): ระบุแนวโน้มหลักของตลาด ไม่ว่าจะเป็นแนวโน้มขาขึ้น (Uptrend), แนวโน้มขาลง (Downtrend) หรือ Sideways การเข้าใจแนวโน้มช่วยในการกำหนดกลยุทธ์การเทรดที่เหมาะสม * Key levels (ระดับราคาสำคัญ): หาระดับราคาแนวรับและแนวต้านที่สำคัญในกรอบเวลา 4 ชั่วโมง ระดับเหล่านี้มักเป็นจุดที่ราคาเคยมีการกลับตัวหรือพักตัวในอดีต และอาจเป็นบริเวณที่ราคาจะตอบสนองอีกครั้งในอนาคต * Supply & Demand (อุปทานและอุปสงค์): วิเคราะห์ความสมดุลระหว่างแรงซื้อ (Demand) และแรงขาย (Supply) ในตลาด โดยพิจารณาจากพฤติกรรมราคาบริเวณแนวรับแนวต้าน และสัญญาณจากเครื่องมือวิเคราะห์อื่นๆ (ถ้าใช้) 2. กรอบเวลา 1 ชั่วโมง (1H): หาจังหวะและบริเวณที่น่าสนใจ เมื่อได้ภาพรวมและทิศทางหลักจากกรอบ 4H แล้ว เราจะย่อยลงมาในกรอบ 1 ชั่วโมง เพื่อหาจังหวะการเทรดที่สอดคล้องกับทิศทางหลัก และมองหารูปแบบราคาที่น่าสนใจ องค์ประกอบสำคัญในกรอบเวลานี้คือ: * Breaks (การทะลุ): สังเกตการทะลุแนวรับแนวต้าน หรือระดับราคาสำคัญในกรอบ 1H ที่สอดคล้องกับทิศทางหลักใน 4H การทะลุเหล่านี้อาจเป็นสัญญาณของการเคลื่อนไหวครั้งใหญ่ของราคา * Reversals (การกลับตัว): มองหารูปแบบการกลับตัวของราคาที่อาจเกิดขึ้นบริเวณระดับราคาสำคัญในกรอบ 1H ซึ่งบ่งบอกถึงจุดสิ้นสุดของแนวโน้มปัจจุบันและเริ่มต้นแนวโน้มใหม่ * OB (Order Blocks): ระบุบริเวณ Order Blocks ในกรอบ 1H ซึ่งเป็นพื้นที่ที่มีการสั่งซื้อขายจำนวนมากในอดีต Order Blocks เหล่านี้มักจะทำหน้าที่เป็นแนวรับแนวต้านในอนาคต * FVG (Fair Value Gaps): มองหา Fair Value Gaps ในกรอบ 1H ซึ่งเป็นช่องว่างของราคาที่เกิดจากการเคลื่อนไหวอย่างรวดเร็ว FVG มักจะเป็นเป้าหมายของราคาในอนาคต เนื่องจากราคาอาจจะกลับมาปิดช่องว่างเหล่านี้ * Liquidity (สภาพคล่อง): ประเมินสภาพคล่องบริเวณระดับราคาที่เราสนใจในกรอบ 1H บริเวณที่มีสภาพคล่องสูงมักจะดึงดูดนักลงทุนรายใหญ่ และอาจทำให้เกิดการเคลื่อนไหวของราคาที่รุนแรง 3. กรอบเวลา 15 นาที (15min): ยืนยันสัญญาณและหาจุดเข้าเทรด ในกรอบเวลา 15 นาที เราจะเน้นการยืนยันสัญญาณการเทรด และหาจุดเข้าเทรดที่แม่นยำ เพื่อลดความเสี่ยงในการเข้าเทรดเร็วเกินไป องค์ประกอบสำคัญในกรอบเวลานี้คือ: * Confirmation (การยืนยัน): รอสัญญาณยืนยันการเคลื่อนไหวของราคาในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบ 1H และ 4H สัญญาณยืนยันอาจมาในรูปแบบของแท่งเทียนกลับตัว, รูปแบบ Chart Patterns, หรือสัญญาณจาก Indicators * จุดเข้าเทรด: เมื่อมีสัญญาณยืนยันที่ชัดเจนในกรอบ 15 นาที และสอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น จึงตัดสินใจเข้าเทรด โดยกำหนด Stop Loss เพื่อจำกัดความเสี่ยง และ Take Profit เพื่อตั้งเป้าหมายในการทำกำไร **กลยุทธ์การเทรด Top-Down Analysis: ขั้นตอนสู่ความสำเร็จ** เพื่อนำ Top-Down Analysis ไปใช้ในการเทรดอย่างมีประสิทธิภาพ เราสามารถทำตามขั้นตอนต่อไปนี้: 1. **เริ่มต้นที่ 4H**: กำหนดทิศทางและแนวโน้มหลัก วิเคราะห์กราฟ 4H เพื่อระบุทิศทางหลักของตลาด แนวโน้ม และระดับราคาสำคัญ ประเมินความสมดุลของ Supply & Demand เพื่อกำหนด Bias การเทรด (เน้นซื้อหรือขาย) 2. **เจาะลึก 1H:** หาจังหวะและบริเวณที่น่าสนใจ เมื่อได้ทิศทางหลักจาก 4H แล้ว ให้ย่อยลงมาดูกราฟ 1H เพื่อหารูปแบบราคาที่น่าสนใจ เช่น การทะลุแนวรับแนวต้าน, รูปแบบการกลับตัว, Order Blocks, Fair Value Gaps และบริเวณที่มีสภาพคล่องสูง 3. **ยืนยันใน 15min:** หาจุดเข้าเทรดที่แม่นยำ รอสัญญาณยืนยันในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น ใช้ Price Action, แท่งเทียน, หรือ Indicators เพื่อยืนยันสัญญาณ และหาจุดเข้าเทรดที่แม่นยำ พร้อมกำหนด Stop Loss และ Take Profit ที่เหมาะสม **ประโยชน์ของการใช้ Top-Down Analysis** * มองเห็นภาพรวมตลาด: ช่วยให้เทรดเดอร์เข้าใจบริบทของตลาดในภาพรวม ไม่หลงทางในรายละเอียดเล็กๆ น้อยๆ * ตัดสินใจเทรดอย่างมีหลักการ: ทำให้การตัดสินใจเทรดมีเหตุผลและมีข้อมูลสนับสนุนมากขึ้น ไม่ใช่แค่การคาดเดา * เพิ่มความแม่นยำในการเทรด: การวิเคราะห์หลายกรอบเวลาช่วยกรองสัญญาณรบกวน และเพิ่มโอกาสในการเข้าเทรดในทิศทางที่ถูกต้อง * ลดความเสี่ยง: ช่วยลดโอกาสในการเทรดสวนทางแนวโน้มหลักของตลาด และช่วยในการกำหนด Stop Loss ที่เหมาะสม **ข้อควรจำและข้อควรระวัง** * ฝึกฝนและสังเกต: Top-Down Analysis ต้องอาศัยการฝึกฝนและการสังเกตกราฟราคาอย่างสม่ำเสมอ เพื่อพัฒนาความเข้าใจและทักษะในการวิเคราะห์ * ปรับใช้ให้เข้ากับสไตล์: ปรับกลยุทธ์ให้เข้ากับสไตล์การเทรดของคุณ และสินทรัพย์ที่คุณเทรด * บริหารความเสี่ยง: ให้ความสำคัญกับการบริหารความเสี่ยงเสมอ กำหนดขนาด Position ที่เหมาะสม และใช้ Stop Loss ทุกครั้ง * ไม่มีกลยุทธ์ใดสมบูรณ์แบบ: Top-Down Analysis เป็นเครื่องมือที่มีประสิทธิภาพ แต่ไม่มีกลยุทธ์ใดที่รับประกันผลกำไร 100% การเทรดมีความเสี่ยง โปรดศึกษาและทำความเข้าใจความเสี่ยงก่อนตัดสินใจลงทุน **สรุป** Top-Down Analysis เป็นกลยุทธ์การเทรดที่ทรงพลัง ซึ่งช่วยให้เทรดเดอร์สามารถวิเคราะห์ตลาดอย่างเป็นระบบ มองภาพรวม และจับจังหวะการเทรดได้อย่างแม่นยำ การนำหลักการของ Top-Down Analysis ไปปรับใช้ในการเทรด จะช่วยเพิ่มประสิทธิภาพในการตัดสินใจ และเพิ่มโอกาสในการประสบความสำเร็จในตลาดการเงินได้อย่างยั่งยืน @ fd208ee8:0fd927c1
2025-02-06 15:58:38## Beginning at the start In my previous article, [The Establishment](https://next-alexandria.gitcitadel.eu/publication?d=the-gitcitadel-blog-the-establishment-3-by-stella-v-1), I answered the question: "How do we form a company?" I realize, now, that I was getting a bit ahead, of myself, as the precursor to a *company* is a *team*, and many people struggle to form teams. So, I will go back to the beginning, and then you can read both articles to the end, and then stop. ## The Initiation The first, and most-difficult step of team formation, is *the initiation*. We know that it must be the most-difficult, as it's the step that carries the highest potential reward, and it's the step that is tried-and-failed most often. (Some people, like Elon Musk or Donald Trump, are born Initiators with excellent follow-through, but this archetype is exceedingly thin on the ground because it requires you to be mildly autistic, have barely-throttled ADHD, and/or tend to megalomania, also popularly known as "toxic masculinity", "CEO personality", or "being a successful military officer".) Someone needs to form a useful, attractive Vision and then motivate other people to help them achieve it. That sounds really easy, but it's actually brutally difficult because * You have to come up with an idea that is coherent, plausible, and inspiring. * You have to be able to communicate that idea to other people and make it appealing to them, by tying it into their own personal goals and desires. * You have to be able to hone and reformulate that idea, constantly, to correct it or to re-motivate the other team members. * You have to defend the idea against detractors, naysayers, and trolls, and you have to do it so vociferously, that it will erode your own popularity among those who disagree with you and open you to personal attacks. * You have to be able to focus on the idea, yourself, for a long stretch of time, and not allow yourself to get bored, lazy, or distracted.  So, just do and be all of those things, and then initiate the team, with the method I will name the *Hatbock Method*. It is so named because of the classic, German initiation ritual, in which an Initiator stands up, loudly defines their Vision and calls into a group "Wer hat Bock?" (roughly, "Who has the hunger/desire?") and whoever responds with "Ich hab Bock." (roughly, "Yes, I hunger for this.") is a part of the team. Then the Initiator says, "Okay, everyone with the hunger, let's sit down together, and discuss this some more." (This "sitting" is literally called a "seating", or "Sitzung", which is the German word for "meeting".) ## The Sitting We now get to the second most difficult part of team formation: figuring out *where to sit*. Most teams get this wrong, repeatedly, and many teams dissolve or fracture under the difficulty of this momentous decision. You would think organizing yourselves online would make this easier ("Oh, we'll just meet online!"), but the number of places available for sitting online are limitless. You can talk your whole Vision into the ground, with laborous discussions and migrations between Chachi, OxChat, Telegram, SimpleX, Slack, Discord, WhatsApp, GitHub, Teams, Coracle, Matrix... you get the idea. Try to keep in mind that the Vision is more important than the seating area, and go with the flow. Simply, find someplace and go there. Worry about it again, at a later date. Don't lose momentum. Sit down and start discussing the Vision, *immediately*.  Now, this next bit is very important: > Do not let anyone outside your team influence where you sit! ...unless they are providing your team with some good, service, or income, that makes choosing their preferred location the superior choice. This is the German *Stammtisch* principle, where a host encourages you to come sit down, regularly, in some particular place, because your sitting there provides them with some benefit: they can overhear your conversations, get you to test out their seating area, sell you refreshments, etc. Your choice of seating, in other words, is a valuable good, and you should only "sell" it to someone who rewards you in measure. They have to reward you because their preferred seating area wasn't your immediate and obvious choice, so there was probably something unappealing or uncertain about the seating area. ## Plan it in Once you've sat down, and finished your rough draft of the Vision, you need to figure out *when to sit*. This is the third most-difficult part of team formation. (Yes, don't worry, it gets easier as it goes along.) The most popular plan is the Wirsehenuns Plan (roughly, "We'll see each other, around.") This can work quite well, if you just want to have a loose collaboration, that calls itself together in an ad hoc fashion, when a team member feels the need. Also known as "@ me, bros". It's not a great plan for more intensive collaboration, as that tends to need a certain amount of velocity, to actually happen, as the speed of movement has a centrifugal effect on the tasks. Team momentum, in other words, creates a sort of gravity, that keeps the team together as a unit. So, for deeper teamwork, I would recommend the Stammtisch variant: name a place and date/time, when you will next meet. Preferably, on a rotating schedule: daily, weekly, last Thursday of the month, etc. And then meet there and then. And discuss amongst yourselves. Set clear, short-term tasks (and assign them to particular people!), medium-term strategies, and longer-term goals. *Write everything down.* Anything not written down, is a suggestion, not an assigned task. If you find your Stammtisch becoming increasingly rewarding and productive, and your goals start moving closer and closer into sight, then you might want to formalize your team structure further, [as a company](https://next-alexandria.gitcitadel.eu/publication?d=the-gitcitadel-blog-the-establishment-3-by-stella-v-1).
@ fd208ee8:0fd927c1
2025-02-06 15:58:38## Beginning at the start In my previous article, [The Establishment](https://next-alexandria.gitcitadel.eu/publication?d=the-gitcitadel-blog-the-establishment-3-by-stella-v-1), I answered the question: "How do we form a company?" I realize, now, that I was getting a bit ahead, of myself, as the precursor to a *company* is a *team*, and many people struggle to form teams. So, I will go back to the beginning, and then you can read both articles to the end, and then stop. ## The Initiation The first, and most-difficult step of team formation, is *the initiation*. We know that it must be the most-difficult, as it's the step that carries the highest potential reward, and it's the step that is tried-and-failed most often. (Some people, like Elon Musk or Donald Trump, are born Initiators with excellent follow-through, but this archetype is exceedingly thin on the ground because it requires you to be mildly autistic, have barely-throttled ADHD, and/or tend to megalomania, also popularly known as "toxic masculinity", "CEO personality", or "being a successful military officer".) Someone needs to form a useful, attractive Vision and then motivate other people to help them achieve it. That sounds really easy, but it's actually brutally difficult because * You have to come up with an idea that is coherent, plausible, and inspiring. * You have to be able to communicate that idea to other people and make it appealing to them, by tying it into their own personal goals and desires. * You have to be able to hone and reformulate that idea, constantly, to correct it or to re-motivate the other team members. * You have to defend the idea against detractors, naysayers, and trolls, and you have to do it so vociferously, that it will erode your own popularity among those who disagree with you and open you to personal attacks. * You have to be able to focus on the idea, yourself, for a long stretch of time, and not allow yourself to get bored, lazy, or distracted.  So, just do and be all of those things, and then initiate the team, with the method I will name the *Hatbock Method*. It is so named because of the classic, German initiation ritual, in which an Initiator stands up, loudly defines their Vision and calls into a group "Wer hat Bock?" (roughly, "Who has the hunger/desire?") and whoever responds with "Ich hab Bock." (roughly, "Yes, I hunger for this.") is a part of the team. Then the Initiator says, "Okay, everyone with the hunger, let's sit down together, and discuss this some more." (This "sitting" is literally called a "seating", or "Sitzung", which is the German word for "meeting".) ## The Sitting We now get to the second most difficult part of team formation: figuring out *where to sit*. Most teams get this wrong, repeatedly, and many teams dissolve or fracture under the difficulty of this momentous decision. You would think organizing yourselves online would make this easier ("Oh, we'll just meet online!"), but the number of places available for sitting online are limitless. You can talk your whole Vision into the ground, with laborous discussions and migrations between Chachi, OxChat, Telegram, SimpleX, Slack, Discord, WhatsApp, GitHub, Teams, Coracle, Matrix... you get the idea. Try to keep in mind that the Vision is more important than the seating area, and go with the flow. Simply, find someplace and go there. Worry about it again, at a later date. Don't lose momentum. Sit down and start discussing the Vision, *immediately*.  Now, this next bit is very important: > Do not let anyone outside your team influence where you sit! ...unless they are providing your team with some good, service, or income, that makes choosing their preferred location the superior choice. This is the German *Stammtisch* principle, where a host encourages you to come sit down, regularly, in some particular place, because your sitting there provides them with some benefit: they can overhear your conversations, get you to test out their seating area, sell you refreshments, etc. Your choice of seating, in other words, is a valuable good, and you should only "sell" it to someone who rewards you in measure. They have to reward you because their preferred seating area wasn't your immediate and obvious choice, so there was probably something unappealing or uncertain about the seating area. ## Plan it in Once you've sat down, and finished your rough draft of the Vision, you need to figure out *when to sit*. This is the third most-difficult part of team formation. (Yes, don't worry, it gets easier as it goes along.) The most popular plan is the Wirsehenuns Plan (roughly, "We'll see each other, around.") This can work quite well, if you just want to have a loose collaboration, that calls itself together in an ad hoc fashion, when a team member feels the need. Also known as "@ me, bros". It's not a great plan for more intensive collaboration, as that tends to need a certain amount of velocity, to actually happen, as the speed of movement has a centrifugal effect on the tasks. Team momentum, in other words, creates a sort of gravity, that keeps the team together as a unit. So, for deeper teamwork, I would recommend the Stammtisch variant: name a place and date/time, when you will next meet. Preferably, on a rotating schedule: daily, weekly, last Thursday of the month, etc. And then meet there and then. And discuss amongst yourselves. Set clear, short-term tasks (and assign them to particular people!), medium-term strategies, and longer-term goals. *Write everything down.* Anything not written down, is a suggestion, not an assigned task. If you find your Stammtisch becoming increasingly rewarding and productive, and your goals start moving closer and closer into sight, then you might want to formalize your team structure further, [as a company](https://next-alexandria.gitcitadel.eu/publication?d=the-gitcitadel-blog-the-establishment-3-by-stella-v-1). @ 3eba5ef4:751f23ae
2025-02-13 09:00:41Security is fundamental to any blockchain. It ensures that all tokens are secure. When talking about a virtual machine and the smart contract platform it forms, security comes in two main aspects: * The code running on the virtual machine must be secure * The virtual machine itself should also be designed to facilitate safer code execution The first aspect often gets sufficient attention. When it comes to [CKB](https://www.nervos.org/), we now encourage developers to write scripts in Rust for maximum security, reserving pure C code only for those who fully understand its risks. Additionally, higher-level languages have been introduced in CKB to strike a better balance between productivity and security. Virtual machine security was a major focus when CKB-VM was originally designed. Many potential risks were addressed at the architectural level, though some—despite thorough research—were still left open. One such issue is **Return-Oriented Programming (ROP)**—a rather ingenious attack. It exploits executable code that has been legitimately loaded into memory, making widely effective protections (e.g., [W^X](https://yakihonne.com/write-article)) futile. It spans multiple architectures and is constantly evolving. Although we’ve spent a great deal of effort in the early days on ROP, we did not implement specific countermeasures to prevent it. Now, with new RISC-V extensions now available, it is the perfect time to introduce design-level protections against ROP. ## Acknowledgments Before diving deeper, we would like to acknowledge Todd Mortimer from the OpenBSD team. His work on ROP mitigations at the OpenBSD kernel in 2018-2019 significantly inspired our research and this article. We highly recommend his [talk](https://www.youtube.com/watch?v=ZvSSHtRv5Mg), slide decks from [AsiaBSDCon 2019](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf) and [EuroBSD 2018](https://www.openbsd.org/papers/eurobsdcon2018-rop.pdf), and this [paper](https://www.openbsd.org/papers/asiabsdcon2019-rop-paper.pdf) for a deeper understanding of ROP. Several examples on x64 ROP attacks in this post are also drawn from his research. ## Typical Attack Workflow While there are many sophisticated [ways](https://www.wired.com/2016/06/clever-attack-uses-sound-computers-fan-steal-data/) of attacks, a common attack on a program typically follows this process: Prepare a [shellcode](https://en.wikipedia.org/wiki/Shellcode)— a piece of binary code to perform specific actions (e.g., running a shell or other programs on the target computer). Exploit one possible vulnerability in the target system, most commonly a [buffer overflow](https://en.wikipedia.org/wiki/Buffer_overflow) attack. The attack could be initiated via a network protocol (such as HTTP) against a remote system, or via command line input to a target program; As the result of the attack, the shellcode is inserted to a designated memory region of the target system and gets executed, allowing the attacker to achieve their goal. The consequences vary, like gaining unauthorized access to sensitive data, destroying certain data/machine, planting malicious programs onto the target for further actions, manipulating control flow. While traditional systems face a wide range of attacks, blockchains run in their own limited and unique runtime environment, rendering many conventional attacks irrelevant. Major blockchain security threats includes: * **Private key security**: Blockchain wallets rely on private keys, which are prime targets for various attacks. * **Smart contract vulnerability**: Poorly written smart contracts contain logic flaws that lead to security risks. * **Virtual machine security**: Attacker may send malicious inputs to a smart contract, causing it to terminate unexpectedly with a success status—despite lacking proper credentials. This post focuses specifically on attacks targeting the blockchain’s virtual machine—in our case—CKB Virtual Machine (CKB-VM) specifically. ## CKB’s Early Approach While it is impossible to predict every attack, disrupting the typical attack workflow is an effective defense strategy. From its inception, CKB-VM has implemented [W^X](https://en.wikipedia.org/wiki/W%5EX) protection: at any given time, any memory location in CKB-VM is either writable (allowing data modification) or executable (allowing data execution)—but never both. Once a memory region is marked as **executable**, it cannot be reverted to **writable** throughout the lifecycle of the current CKB-VM instance. Only writable memory location can be **frozen** to executable. This design significantly disrupts the typical attack workflow. For shellcode to execute on CKB-VM, it must reside in **executable** memory. However, an attacker can only provide shellcode as part of program inputs, which are loaded into **writable** memory. As long as a CKB script does not voluntarily mark input data as **executable** (a highly unlikely scenario), the shellcode remains inert. Additionally, attempting to overwrite existing **executable** shellcode is also futile, since executable memory region is unwritable, and cannot be converted back to writable. This way, W^X is a well-established security technique widely used in modern hardwares, operating systems, and virtual machines. Although it cannot prevent all possible attacks, W^X effectively shields many by breaking the standard attack workflow. Even if an attacker successfully injects shellcode into a target machine, the attack is incomplete due to the inability to execute it. ## Understanding ROP While W^X is effective, it does not solve all our problems. This leads to the topic of this post: **Return-oriented Programming (ROP)**. Instead of explicitly injecting new code, ROP exploits executable code that already resides in the target machine’s memory. Essentially, ROP builds a shellcode by chaining existing code snippets together that were never intended to function as such. It may sound like a fantasy, but as we shall see from the following examples, ROP is a practical and effective attack technique. To understand ROP, we must first examine modern CPU architecture and memory layout. While assembly instructions vary in representations and lengths, they are put together in memory one after another as a stream of bytes:  *Image [Source](https://www.quora.com/Is-assembly-language-a-source-code-or-object-code)* As seen in the above example, different assembly instructions come in different lengths. For x86-64 ISA, an instruction can range from 1 to 7 bytes (RISC ISAs such as ARM or RISC-V have more uniform instruction lengths—we will discuss it later). But in memory, instructions are stored sequentially without gaps. This means that with a stream of bytes alone, we really don’t know what instructions the stream of bytes consist of. In the above example, meaningful assembly instructions emerge only when we start decoding from the `B8` byte. In a different occasion, assuming we know elsewhere that `B8 22 11` bytes at the front are for certain magic flags, the decoding would start from `00` byte, yielding a totally different instruction set.  *Image [Source](https://www.quora.com/Is-assembly-language-a-source-code-or-object-code)* It is really the combination of a special program counter (`PC`) register from the CPU and the current memory stream, jointly determine the instructions the CPU executes. Depending on each different ISA or hardware, a booting process initializes a CPU’s `PC` register to a pre-defined value, then loads up instructions from this pre-defined address, and initializes everything related to the operating system. When a user launches a new program, the metadata for each program will contain an `entrypoint` address, where OS sets the CPU’s `PC` register to, in order to start executing the program. It is suffice to say that maintaining a proper `PC` value is a critical job to ensure a computer’s proper function. An invalid `PC` value might lead to a CPU malfunction at best, or at worst, leaking sensitive information or granting attackers unauthorized access. ### Forming an ROP Attack Via ROP Gadgets Let’s look at the following byte instruction stream in a x86-64 CPU: ``` 8a 5d c3 movb -61(%rbp), %bl ``` This 3-byte represents a `mov` instruction: it takes the address of `rbp` register, adds an offset of `-61`, then uses the result as a memory address to load 1 byte data, and finally sets the loaded data to `bl` register. However, if we ignore `8a` and only look at `5b c3` here, it actually represents a different instruction set: ``` 5d popq %rbp c3 retq ``` This byte sequence contains two instructions: * Pop 8-byte value from stack, and use it to set `rbp` register * Pop 8-byte value from stack, and use it to set `PC` register, so we continue executing from the new location We've briefly discussed that shellcode only fulfills a certain task required by the attacker. In fact, the most common type of shellcode simply construct a new shell, where the attacker can execute more operations. Such shellcode can be represented in the following C pseudocode to run a new command via the `execve` syscall: ``` execve(“/bin/sh”, NULL, NULL); ``` To execute this on an x86-64 CPU, the following actions are needed for a syscall: * `rax` register: must contain the syscall number, for `execve`, it is `59` * `rdi`, `rsi`, `rdx` registers: hold the first 3 arguments to the syscall. In this case, `rdi` holds a pointer to the C string `/bin/sh`; `rsi` and `rdx` must be zero. * The `syscall` instruction (or typically `int 80h` on x64) shall be executed A typical shellcode would be a packed assembly sequence directly doing all of the above instructions. In contrast, ROP attack looks for the following sequences: ``` # Those can set the value of different registers from values on the stack pop %rax; ret pop %rdi; ret pop %rsi; ret pop %rdx; ret # Finally, trigger the syscall syscall ``` Each of these small code sequences, are conventionally callled **ROP gadgets**. An attacker searches for these gadgets in the target program or system libraries (such as libc). Once these required gadgets are obtained, the attacker pieces together a sequence of data, much like the following:  With the prepared data sequence, the attacker can exploit a vulnerability in the target computer or program, such as typical buffer overflow attack. During this process, the attacker performs three key actions: * Pushes (or overwrites existing data) the crafted data sequence to the stack * Sets the stack pointer (top of the stack) to `X + 64` * Sets the `PC` register to the address of a code sequence, `pop %rax; ret` in the existing program or libc memory space Now the attack proceeds step by step as follows: 1. The CPU runs `pop %rax; ret`. With the stack pointer pointing to `X + 64`, the CPU pops `59` from the stack and sets `rax` register to `59`. It then pops the address to code sequence `pop %rdi; ret` from the stack, and sets `PC` to this value; 2. The CPU runs `pop %rdi; ret`. With the stack pointer pointing to `X + 48`, the CPU pops value `X`, pointing to the C string `/bin/sh` from the stack, and sets `rdi` register to `X`. It then pops the address to code sequence `pop %rsi; ret` from the stack, and sets `PC` to this value; 3. The CPU runs `pop %rsi; ret`. With the stack pointer pointing to `X + 32`, the CPU pops `0` from the stack and sets `rsi` register to `0`. It then pops the address to code sequence `pop %rdx; ret` from the stack, and sets `PC` to this value; 4. The CPU runs `pop %rdx; ret`. With the stack pointer pointing to `X + 16`, the CPU pops `0` from the stack and sets `rdx` register to `0`. It then pops the address to code sequence `syscall` from the stack, and sets `P`C to this value; 5. The CPU runs `syscall`. At this point, `rax` holds `59`, `rdi` points to `/bin/sh`, and both `rsi` and `rdx` are zero, the CPU invokes `execve("/bin/sh, NULL, NULL);`, granting the attacker a shell for further manipulations. This sequence of ROP gadgets, referred to as **ROP chains**, demonstrates how a complete ROP attack works. Two key takeaways are: * **ROP does not inject new code**. Instead, it injects data into the stack and leverages the existing code loaded in memory and marked them as executable. W^X protections hence cannot prevent ROP attacks. * **Attackers can mine ROP gadgets from the [libc](https://en.wikipedia.org/wiki/C_standard_library) library**. This is because modern computers employs [protection rings](https://en.wikipedia.org/wiki/Protection_ring) as a way for privilege encapsulations: on x86-64 computers, programs normally run at ring level 3, while libc runs at ring level 1. Lower ring levels have higher privileges, meaning that even if a program misbehaves, its capacities are limited at ring level 3. However, by using ROP gadgets in the libc library which runs at ring level 1, ROP attacks can have higher privileges and execute more damaging operations then normal shellcodes. Note that the above examples simply show the most basic ROP gadgets. In reality, ROP gadgets come in all kinds of forms. Since they come from compiler outputs, they can be combined in the least expected way, and can vary the forms as new compiler optimizations come out. Numerous tools (e.g., [ropper](https://scoding.de/ropper/), [ropr](https://github.com/Ben-Lichtman/ropr)) and research papers (e.g., *[Experiments on ROP Attack with Various Instruction Set Architectures](https://dl.yumulab.org/papers/42/paper.pdf)*, *[ROPGMN](https://www.sciencedirect.com/science/article/abs/pii/S0167739X24005314)*, *[Detecting and Preventing ROP Attacks using Machine Learning on ARM](https://www.infosun.fim.uni-passau.de/ch/publications/compsac23.pdf)*, *[KROP](https://arxiv.org/pdf/2406.11880)* ) keep coming out, making it almost impossible to enumerate all possible ROP gadget combinations. ### ROP on ARM & RISC-V ROP attacks are not limited to CISC architectures, where instructions vary in length. They also affect RISC designs, such as [ARM](https://developer.arm.com/documentation/102433/0200/Return-oriented-programming) and [RISC-V](https://pure.royalholloway.ac.uk/ws/portalfiles/portal/37157938/ROP_RISCV.pdf). Take the following sequence for example: ``` 13 4f 83 23 0b 00 ``` Decoding from the start, the first four bytes represent `xori t5,t1,568` following the RISC-V ISA. But if we skip the first two, the latter four represent `lw t2,0(s6)`. This illustrates that a byte stream interpretation also requires `PC` register in a RISC design such as RISC-V. As a result, one can find ROP gadgets from a RISC-V program as well. ### ROP on CKB-VM CKB’s RISC-V machine operates in a more restricted environment: for programs running on CKB, there are no `execve` syscalls to hijack a running shell, and all runtime states are publicly visible on a public blockchain like CKB. However, ROP attacks can still occur on CKB: one could construct an ROP chain that sets `a0` to `0`, `a7` to `93`, then executes `ecall`. This causes CKB-VM to immediately return with a success code (`0`), potentially allowing a script to pass validation when it should have failed—such as a lock script succeeding without a valid signature. ### Short Recap Let’s briefly recap what we’ve learned so far: * ROP attacks utilize existing executable code for malicious purposes. W^X cannot prevent ROP. * ROP is possible across multiple architecture, including x86-64, ARM, RISC-V, and CKB. * The landscape of ROP is constantly evolving. With new tools, techniques, and research emerging regularly, it’s impossible to foresee all ROP gadgets. ROP has been extensively studied over the years, leading to various mitigation strategies, which can be broadly categorized into two main approaches: * **Software Solutions**: Covering techniques like rewriting code sequences and implementing Retguard to prevent the creation of ROP gadgets * **Hardware Solutions**: Introducing additional CPU instructions with Control Flow Integrity (CFI) checks to safeguard control flow. I’ll explore these strategies in greater detail in the following sections. ## Software Solutions to Mitigate ROP ### Rewriting Sequence Certain instruction sequences are often targeted to form ROP gadgets. To prevent ROP, one approach is to alter the compiler, so that such sequences can never be generated. Take the following example: ``` 89 c3 mov %eax,%ebx 90. ``` In x86-64, `c3` represents the `ret` instruction, making it a potential target for ROP gadgets. We can rewrite it into the following equivalent sequence: ``` 48 87 d8 xchgq %rbx, %rax 89 d8 movl %ebx, %eax 48 87 d8 xchgq %rbx, %rax ``` The new sequence lacks `c3` byte at the expense of more bytes and more executed instructions. However, it is really up to real benchmarks to see if this causes noticeable overhead. Further analysis has revealed that the `rbx` register in x86-64 is often the source of ROP gadgets, due to the way Intel encodes x86-64 instructions. Hence, the OpenBSD team decided to avoid `rbx` register wherever possible, reducing the number of potential ROP gadgets. Again, this approach comes at the cost of having bigger code fragments, more instructions to execute, and an additional patched compiler. While OpenBSD has integrated these changes into its distribution, other environments must weigh the benefits against the costs. For a deeper dive, I would strongly recommend Todd Mortimer’s [work](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf). ### Retguard’s Solution: Prologue and Epilogue Todd Mortimer also introduced Retguard in this [work](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf) for securing OpenBSD known. ROP attacks typically occur when you enter a function `foo`, but the stack was manipulated, so the CPU exits to another code fragment that is not `foo`. What if to verify that, at each function exit, it is the same function for exiting and entering? Retguard introduces two components to perform this task: * **Prologue**: A prologue is inserted to each function’s entry, taking two inputs: - - A `cookie` value, a random data assigned for this particular function. - - The return address, where to jump to when current function exits—as inputs. The prologue computes the XOR value of these two, and stores the result into the current function’s [frame](https://en.wikipedia.org/wiki/Call_stack#Stack_and_frame_pointers) section, a dedicated memory region designated to the current function to hold data, separated from the stack. * **Epilogue**: An epilogue is inserted to the location where a function might exit. It takes two inputs: - - The saved XOR value from the prologue in the frame section - - The return address it now can access to (most likely popped from the stack in x64 machine, or read from a special `RA` register in RISC design) The epilogue computes the XOR of these two. If the result matches the original `cookie`, execution proceeds. Otherwise, the epilogue halts the program, signaling an error. This prologue-epilogue mechanism in Retguard guards the call stack from tampering. At a noticeable but acceptable cost (both in performance and code size), Retguard eliminates a significant number of ROP gadgets from the OpenBSD kernel. Like other software-based mitigations, it requires a patched compiler, and it is up to each environment to decide if such technique shall be employed. ## Hardware Advancements to Mitigate ROP In addition to software solutions, hardware-based defenses have also been developed. For instance, Intel has introduced [Indirect Branch Tracking](https://edc.intel.com/content/www/us/en/design/ipla/software-development-platforms/client/platforms/alder-lake-desktop/12th-generation-intel-core-processors-datasheet-volume-1-of-2/007/indirect-branch-tracking/?language=en) feature starting with its 12th generation core processors, using a new instruction `endbr32` or `endbr64` added at every location the program might jump to or call into. When the CPU executes a jump/call, it asserts that the target location is a proper `endbr32` / `endbr64` instruction, before updating the program counter `PC` register to proper values. Otherwise, the CPU halts to terminate the program. This ensures that all control flows will follow the intended way, preventing ROP attacks from redirecting execution arbitrary locations. Modern OSes have already extensively leveraged `endbr32` / `endbr64` instructions. Ubuntu 24.04, for instance, has included these instructions in its packages: ``` $ objdump -d /bin/bash | head -n 50 /bin/bash: file format elf64-x86-64 Disassembly of section .init: 0000000000030000 <.init>: 30000: f3 0f 1e fa endbr64 30004: 48 83 ec 08 sub $0x8,%rsp 30008: 48 8b 05 d9 7e 12 00 mov 0x127ed9(%rip),%rax # 157ee8 <__gmon_start__@Base> 3000f: 48 85 c0 test %rax,%rax 30012: 74 02 je 30016 <unlink@plt-0xe1a> 30014: ff d0 call *%rax 30016: 48 83 c4 08 add $0x8,%rsp 3001a: c3 ret Disassembly of section .plt: 0000000000030020 <.plt>: 30020: ff 35 a2 76 12 00 push 0x1276a2(%rip) # 1576c8 <o_options@@Base+0x1cc8> 30026: ff 25 a4 76 12 00 jmp *0x1276a4(%rip) # 1576d0 <o_options@@Base+0x1cd0> 3002c: 0f 1f 40 00 nopl 0x0(%rax) 30030: f3 0f 1e fa endbr64 30034: 68 00 00 00 00 push $0x0 30039: e9 e2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3003e: 66 90 xchg %ax,%ax 30040: f3 0f 1e fa endbr64 30044: 68 01 00 00 00 push $0x1 30049: e9 d2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3004e: 66 90 xchg %ax,%ax 30050: f3 0f 1e fa endbr64 30054: 68 02 00 00 00 push $0x2 30059: e9 c2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3005e: 66 90 xchg %ax,%ax 30060: f3 0f 1e fa endbr64 30064: 68 03 00 00 00 push $0x3 30069: e9 b2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3006e: 66 90 xchg %ax,%ax 30070: f3 0f 1e fa endbr64 30074: 68 04 00 00 00 push $0x4 30079: e9 a2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3007e: 66 90 xchg %ax,%ax 30080: f3 0f 1e fa endbr64 30084: 68 05 00 00 00 push $0x5 30089: e9 92 ff ff ff jmp 30020 <unlink@plt-0xe10> 3008e: 66 90 xchg %ax,%ax 30090: f3 0f 1e fa endbr64 30094: 68 06 00 00 00 push $0x6 30099: e9 82 ff ff ff jmp 30020 <unlink@plt-0xe10> 3009e: 66 90 xchg %ax,%ax ``` The `endbr32` / `endbr64` instructions has been carefully designed, so they are `nop` instructions—meaning they can do nothing at all—on CPUs prior to their introductions. Having them doesn't have any effect on older CPUs but enhances security on supported hardware. ## RISC-V’s Latest Achievements: CFI Extension The above mitigations against ROP fall into two categories: * **Compiler Modifications**: Can generate more secure binary assembly code. * **Additional CPU instructions**: Coming with Control Flow Integrity (CFI) checks to prevent exploitation Back to the beginning of designing CKB-VM, we throughly studied ROP and recognized that a vulnerability in a CKB script could potentially open the door to ROP attacks. However, we eventually did not introduce any specific mitigation against ROP in CKB-VM. Our decision was to stay aligned with the RISC-V ecosystem, avoiding shipping any custom RISC-V spec with additional instructions that would require a patched compiler. Nor do we want to maintain our own compiler set, eliminating the potential that any RISC-V-compliant compiler shall be able to produce CKB script. As the result, we shipped the first version of CKB-VM without ROP mitigations, but that does not mean we’ve ignore this issue: * We’ve [reached out](https://groups.google.com/a/groups.riscv.org/g/isa-dev/c/LyZzjJG7_18/m/pCSnKZPdBAAJ) to the RISC-V community for possible extension similar to Intel’s solution, and kept monitoring advancements in this field; * We’ve been watching over progress and writing secure CKB scripts. Since ROP relies on existing vulnerabilities, secure CKB scripts can kept ROP purely theoretical. We were thrilled when the **RISC-V CFI (Control-Flow Integrity) Extension** was officialy [ratified](https://github.com/riscv/riscv-cfi/releases/tag/v1.0) in July 2024. Designed by the brilliant minds from the RISC-V Foundation, this extension directly addresses ROP attacks with two key features: * `Zicfilp` extension introduces **landing pad**: Resembles Intel’s `endbr32` / `endbr64` to ensure that the CPU can only jump to valid, permitted targets. * `Zicfiss` extension introduces **shadow stack** with a series of instructions:. Offers a hardware solution similar to Retguard, where CPU ensures the control flow integrity or simply puts the call stack, preventing tampering throughout execution. Together, these features offer the state-of-the-art mitigations against ROP. More importantly, RISC-V CFI is now an official extension, meaning all future RISC-V CPUs, compilers, and tools will support this extension. In fact, LLVM 19 has already [supported](https://releases.llvm.org/19.1.0/docs/ReleaseNotes.html#changes-to-the-risc-v-backend), and I believe other compilers and tools will follow soon. Once fully adopted, CKB script developers can simply turn them on like a switch during code compilation. Without modifying the code, they can enjoy the security provided by RISC-V CFI extensions. Even if a vulnerability exists in a CKB script, these built-in enforcements can prevent it from being exploited. ## Final Words Security is complex. While we strive for maximum security, certain design principles might get in the way from introducing specific mitigations. ROP is a prime example: while we did learn much about it early on, implementing the best mitigations needs proper timing. Now the time has come. We are happy to introduce RISC-V CFI in CKB’s next hardfork, bringing stronger security for everyone. *** ✍🏻 Written by Xuejie Xiao His previous posts include: * [A Journey Optimizing CKB Smart Contract: Porting Bitcoin as an Example](https://blog.cryptape.com/a-journey-optimizing-ckb-smart-contract) * [Optimizing C++ Code for CKB-VM: Porting Bitcoin as an Example](https://blog.cryptape.com/optimizing-c-code-for-ckb-vm) Find more in his personal website [Less is More](https://xuejie.space/).
@ 3eba5ef4:751f23ae
2025-02-13 09:00:41Security is fundamental to any blockchain. It ensures that all tokens are secure. When talking about a virtual machine and the smart contract platform it forms, security comes in two main aspects: * The code running on the virtual machine must be secure * The virtual machine itself should also be designed to facilitate safer code execution The first aspect often gets sufficient attention. When it comes to [CKB](https://www.nervos.org/), we now encourage developers to write scripts in Rust for maximum security, reserving pure C code only for those who fully understand its risks. Additionally, higher-level languages have been introduced in CKB to strike a better balance between productivity and security. Virtual machine security was a major focus when CKB-VM was originally designed. Many potential risks were addressed at the architectural level, though some—despite thorough research—were still left open. One such issue is **Return-Oriented Programming (ROP)**—a rather ingenious attack. It exploits executable code that has been legitimately loaded into memory, making widely effective protections (e.g., [W^X](https://yakihonne.com/write-article)) futile. It spans multiple architectures and is constantly evolving. Although we’ve spent a great deal of effort in the early days on ROP, we did not implement specific countermeasures to prevent it. Now, with new RISC-V extensions now available, it is the perfect time to introduce design-level protections against ROP. ## Acknowledgments Before diving deeper, we would like to acknowledge Todd Mortimer from the OpenBSD team. His work on ROP mitigations at the OpenBSD kernel in 2018-2019 significantly inspired our research and this article. We highly recommend his [talk](https://www.youtube.com/watch?v=ZvSSHtRv5Mg), slide decks from [AsiaBSDCon 2019](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf) and [EuroBSD 2018](https://www.openbsd.org/papers/eurobsdcon2018-rop.pdf), and this [paper](https://www.openbsd.org/papers/asiabsdcon2019-rop-paper.pdf) for a deeper understanding of ROP. Several examples on x64 ROP attacks in this post are also drawn from his research. ## Typical Attack Workflow While there are many sophisticated [ways](https://www.wired.com/2016/06/clever-attack-uses-sound-computers-fan-steal-data/) of attacks, a common attack on a program typically follows this process: Prepare a [shellcode](https://en.wikipedia.org/wiki/Shellcode)— a piece of binary code to perform specific actions (e.g., running a shell or other programs on the target computer). Exploit one possible vulnerability in the target system, most commonly a [buffer overflow](https://en.wikipedia.org/wiki/Buffer_overflow) attack. The attack could be initiated via a network protocol (such as HTTP) against a remote system, or via command line input to a target program; As the result of the attack, the shellcode is inserted to a designated memory region of the target system and gets executed, allowing the attacker to achieve their goal. The consequences vary, like gaining unauthorized access to sensitive data, destroying certain data/machine, planting malicious programs onto the target for further actions, manipulating control flow. While traditional systems face a wide range of attacks, blockchains run in their own limited and unique runtime environment, rendering many conventional attacks irrelevant. Major blockchain security threats includes: * **Private key security**: Blockchain wallets rely on private keys, which are prime targets for various attacks. * **Smart contract vulnerability**: Poorly written smart contracts contain logic flaws that lead to security risks. * **Virtual machine security**: Attacker may send malicious inputs to a smart contract, causing it to terminate unexpectedly with a success status—despite lacking proper credentials. This post focuses specifically on attacks targeting the blockchain’s virtual machine—in our case—CKB Virtual Machine (CKB-VM) specifically. ## CKB’s Early Approach While it is impossible to predict every attack, disrupting the typical attack workflow is an effective defense strategy. From its inception, CKB-VM has implemented [W^X](https://en.wikipedia.org/wiki/W%5EX) protection: at any given time, any memory location in CKB-VM is either writable (allowing data modification) or executable (allowing data execution)—but never both. Once a memory region is marked as **executable**, it cannot be reverted to **writable** throughout the lifecycle of the current CKB-VM instance. Only writable memory location can be **frozen** to executable. This design significantly disrupts the typical attack workflow. For shellcode to execute on CKB-VM, it must reside in **executable** memory. However, an attacker can only provide shellcode as part of program inputs, which are loaded into **writable** memory. As long as a CKB script does not voluntarily mark input data as **executable** (a highly unlikely scenario), the shellcode remains inert. Additionally, attempting to overwrite existing **executable** shellcode is also futile, since executable memory region is unwritable, and cannot be converted back to writable. This way, W^X is a well-established security technique widely used in modern hardwares, operating systems, and virtual machines. Although it cannot prevent all possible attacks, W^X effectively shields many by breaking the standard attack workflow. Even if an attacker successfully injects shellcode into a target machine, the attack is incomplete due to the inability to execute it. ## Understanding ROP While W^X is effective, it does not solve all our problems. This leads to the topic of this post: **Return-oriented Programming (ROP)**. Instead of explicitly injecting new code, ROP exploits executable code that already resides in the target machine’s memory. Essentially, ROP builds a shellcode by chaining existing code snippets together that were never intended to function as such. It may sound like a fantasy, but as we shall see from the following examples, ROP is a practical and effective attack technique. To understand ROP, we must first examine modern CPU architecture and memory layout. While assembly instructions vary in representations and lengths, they are put together in memory one after another as a stream of bytes:  *Image [Source](https://www.quora.com/Is-assembly-language-a-source-code-or-object-code)* As seen in the above example, different assembly instructions come in different lengths. For x86-64 ISA, an instruction can range from 1 to 7 bytes (RISC ISAs such as ARM or RISC-V have more uniform instruction lengths—we will discuss it later). But in memory, instructions are stored sequentially without gaps. This means that with a stream of bytes alone, we really don’t know what instructions the stream of bytes consist of. In the above example, meaningful assembly instructions emerge only when we start decoding from the `B8` byte. In a different occasion, assuming we know elsewhere that `B8 22 11` bytes at the front are for certain magic flags, the decoding would start from `00` byte, yielding a totally different instruction set.  *Image [Source](https://www.quora.com/Is-assembly-language-a-source-code-or-object-code)* It is really the combination of a special program counter (`PC`) register from the CPU and the current memory stream, jointly determine the instructions the CPU executes. Depending on each different ISA or hardware, a booting process initializes a CPU’s `PC` register to a pre-defined value, then loads up instructions from this pre-defined address, and initializes everything related to the operating system. When a user launches a new program, the metadata for each program will contain an `entrypoint` address, where OS sets the CPU’s `PC` register to, in order to start executing the program. It is suffice to say that maintaining a proper `PC` value is a critical job to ensure a computer’s proper function. An invalid `PC` value might lead to a CPU malfunction at best, or at worst, leaking sensitive information or granting attackers unauthorized access. ### Forming an ROP Attack Via ROP Gadgets Let’s look at the following byte instruction stream in a x86-64 CPU: ``` 8a 5d c3 movb -61(%rbp), %bl ``` This 3-byte represents a `mov` instruction: it takes the address of `rbp` register, adds an offset of `-61`, then uses the result as a memory address to load 1 byte data, and finally sets the loaded data to `bl` register. However, if we ignore `8a` and only look at `5b c3` here, it actually represents a different instruction set: ``` 5d popq %rbp c3 retq ``` This byte sequence contains two instructions: * Pop 8-byte value from stack, and use it to set `rbp` register * Pop 8-byte value from stack, and use it to set `PC` register, so we continue executing from the new location We've briefly discussed that shellcode only fulfills a certain task required by the attacker. In fact, the most common type of shellcode simply construct a new shell, where the attacker can execute more operations. Such shellcode can be represented in the following C pseudocode to run a new command via the `execve` syscall: ``` execve(“/bin/sh”, NULL, NULL); ``` To execute this on an x86-64 CPU, the following actions are needed for a syscall: * `rax` register: must contain the syscall number, for `execve`, it is `59` * `rdi`, `rsi`, `rdx` registers: hold the first 3 arguments to the syscall. In this case, `rdi` holds a pointer to the C string `/bin/sh`; `rsi` and `rdx` must be zero. * The `syscall` instruction (or typically `int 80h` on x64) shall be executed A typical shellcode would be a packed assembly sequence directly doing all of the above instructions. In contrast, ROP attack looks for the following sequences: ``` # Those can set the value of different registers from values on the stack pop %rax; ret pop %rdi; ret pop %rsi; ret pop %rdx; ret # Finally, trigger the syscall syscall ``` Each of these small code sequences, are conventionally callled **ROP gadgets**. An attacker searches for these gadgets in the target program or system libraries (such as libc). Once these required gadgets are obtained, the attacker pieces together a sequence of data, much like the following:  With the prepared data sequence, the attacker can exploit a vulnerability in the target computer or program, such as typical buffer overflow attack. During this process, the attacker performs three key actions: * Pushes (or overwrites existing data) the crafted data sequence to the stack * Sets the stack pointer (top of the stack) to `X + 64` * Sets the `PC` register to the address of a code sequence, `pop %rax; ret` in the existing program or libc memory space Now the attack proceeds step by step as follows: 1. The CPU runs `pop %rax; ret`. With the stack pointer pointing to `X + 64`, the CPU pops `59` from the stack and sets `rax` register to `59`. It then pops the address to code sequence `pop %rdi; ret` from the stack, and sets `PC` to this value; 2. The CPU runs `pop %rdi; ret`. With the stack pointer pointing to `X + 48`, the CPU pops value `X`, pointing to the C string `/bin/sh` from the stack, and sets `rdi` register to `X`. It then pops the address to code sequence `pop %rsi; ret` from the stack, and sets `PC` to this value; 3. The CPU runs `pop %rsi; ret`. With the stack pointer pointing to `X + 32`, the CPU pops `0` from the stack and sets `rsi` register to `0`. It then pops the address to code sequence `pop %rdx; ret` from the stack, and sets `PC` to this value; 4. The CPU runs `pop %rdx; ret`. With the stack pointer pointing to `X + 16`, the CPU pops `0` from the stack and sets `rdx` register to `0`. It then pops the address to code sequence `syscall` from the stack, and sets `P`C to this value; 5. The CPU runs `syscall`. At this point, `rax` holds `59`, `rdi` points to `/bin/sh`, and both `rsi` and `rdx` are zero, the CPU invokes `execve("/bin/sh, NULL, NULL);`, granting the attacker a shell for further manipulations. This sequence of ROP gadgets, referred to as **ROP chains**, demonstrates how a complete ROP attack works. Two key takeaways are: * **ROP does not inject new code**. Instead, it injects data into the stack and leverages the existing code loaded in memory and marked them as executable. W^X protections hence cannot prevent ROP attacks. * **Attackers can mine ROP gadgets from the [libc](https://en.wikipedia.org/wiki/C_standard_library) library**. This is because modern computers employs [protection rings](https://en.wikipedia.org/wiki/Protection_ring) as a way for privilege encapsulations: on x86-64 computers, programs normally run at ring level 3, while libc runs at ring level 1. Lower ring levels have higher privileges, meaning that even if a program misbehaves, its capacities are limited at ring level 3. However, by using ROP gadgets in the libc library which runs at ring level 1, ROP attacks can have higher privileges and execute more damaging operations then normal shellcodes. Note that the above examples simply show the most basic ROP gadgets. In reality, ROP gadgets come in all kinds of forms. Since they come from compiler outputs, they can be combined in the least expected way, and can vary the forms as new compiler optimizations come out. Numerous tools (e.g., [ropper](https://scoding.de/ropper/), [ropr](https://github.com/Ben-Lichtman/ropr)) and research papers (e.g., *[Experiments on ROP Attack with Various Instruction Set Architectures](https://dl.yumulab.org/papers/42/paper.pdf)*, *[ROPGMN](https://www.sciencedirect.com/science/article/abs/pii/S0167739X24005314)*, *[Detecting and Preventing ROP Attacks using Machine Learning on ARM](https://www.infosun.fim.uni-passau.de/ch/publications/compsac23.pdf)*, *[KROP](https://arxiv.org/pdf/2406.11880)* ) keep coming out, making it almost impossible to enumerate all possible ROP gadget combinations. ### ROP on ARM & RISC-V ROP attacks are not limited to CISC architectures, where instructions vary in length. They also affect RISC designs, such as [ARM](https://developer.arm.com/documentation/102433/0200/Return-oriented-programming) and [RISC-V](https://pure.royalholloway.ac.uk/ws/portalfiles/portal/37157938/ROP_RISCV.pdf). Take the following sequence for example: ``` 13 4f 83 23 0b 00 ``` Decoding from the start, the first four bytes represent `xori t5,t1,568` following the RISC-V ISA. But if we skip the first two, the latter four represent `lw t2,0(s6)`. This illustrates that a byte stream interpretation also requires `PC` register in a RISC design such as RISC-V. As a result, one can find ROP gadgets from a RISC-V program as well. ### ROP on CKB-VM CKB’s RISC-V machine operates in a more restricted environment: for programs running on CKB, there are no `execve` syscalls to hijack a running shell, and all runtime states are publicly visible on a public blockchain like CKB. However, ROP attacks can still occur on CKB: one could construct an ROP chain that sets `a0` to `0`, `a7` to `93`, then executes `ecall`. This causes CKB-VM to immediately return with a success code (`0`), potentially allowing a script to pass validation when it should have failed—such as a lock script succeeding without a valid signature. ### Short Recap Let’s briefly recap what we’ve learned so far: * ROP attacks utilize existing executable code for malicious purposes. W^X cannot prevent ROP. * ROP is possible across multiple architecture, including x86-64, ARM, RISC-V, and CKB. * The landscape of ROP is constantly evolving. With new tools, techniques, and research emerging regularly, it’s impossible to foresee all ROP gadgets. ROP has been extensively studied over the years, leading to various mitigation strategies, which can be broadly categorized into two main approaches: * **Software Solutions**: Covering techniques like rewriting code sequences and implementing Retguard to prevent the creation of ROP gadgets * **Hardware Solutions**: Introducing additional CPU instructions with Control Flow Integrity (CFI) checks to safeguard control flow. I’ll explore these strategies in greater detail in the following sections. ## Software Solutions to Mitigate ROP ### Rewriting Sequence Certain instruction sequences are often targeted to form ROP gadgets. To prevent ROP, one approach is to alter the compiler, so that such sequences can never be generated. Take the following example: ``` 89 c3 mov %eax,%ebx 90. ``` In x86-64, `c3` represents the `ret` instruction, making it a potential target for ROP gadgets. We can rewrite it into the following equivalent sequence: ``` 48 87 d8 xchgq %rbx, %rax 89 d8 movl %ebx, %eax 48 87 d8 xchgq %rbx, %rax ``` The new sequence lacks `c3` byte at the expense of more bytes and more executed instructions. However, it is really up to real benchmarks to see if this causes noticeable overhead. Further analysis has revealed that the `rbx` register in x86-64 is often the source of ROP gadgets, due to the way Intel encodes x86-64 instructions. Hence, the OpenBSD team decided to avoid `rbx` register wherever possible, reducing the number of potential ROP gadgets. Again, this approach comes at the cost of having bigger code fragments, more instructions to execute, and an additional patched compiler. While OpenBSD has integrated these changes into its distribution, other environments must weigh the benefits against the costs. For a deeper dive, I would strongly recommend Todd Mortimer’s [work](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf). ### Retguard’s Solution: Prologue and Epilogue Todd Mortimer also introduced Retguard in this [work](https://www.openbsd.org/papers/asiabsdcon2019-rop-slides.pdf) for securing OpenBSD known. ROP attacks typically occur when you enter a function `foo`, but the stack was manipulated, so the CPU exits to another code fragment that is not `foo`. What if to verify that, at each function exit, it is the same function for exiting and entering? Retguard introduces two components to perform this task: * **Prologue**: A prologue is inserted to each function’s entry, taking two inputs: - - A `cookie` value, a random data assigned for this particular function. - - The return address, where to jump to when current function exits—as inputs. The prologue computes the XOR value of these two, and stores the result into the current function’s [frame](https://en.wikipedia.org/wiki/Call_stack#Stack_and_frame_pointers) section, a dedicated memory region designated to the current function to hold data, separated from the stack. * **Epilogue**: An epilogue is inserted to the location where a function might exit. It takes two inputs: - - The saved XOR value from the prologue in the frame section - - The return address it now can access to (most likely popped from the stack in x64 machine, or read from a special `RA` register in RISC design) The epilogue computes the XOR of these two. If the result matches the original `cookie`, execution proceeds. Otherwise, the epilogue halts the program, signaling an error. This prologue-epilogue mechanism in Retguard guards the call stack from tampering. At a noticeable but acceptable cost (both in performance and code size), Retguard eliminates a significant number of ROP gadgets from the OpenBSD kernel. Like other software-based mitigations, it requires a patched compiler, and it is up to each environment to decide if such technique shall be employed. ## Hardware Advancements to Mitigate ROP In addition to software solutions, hardware-based defenses have also been developed. For instance, Intel has introduced [Indirect Branch Tracking](https://edc.intel.com/content/www/us/en/design/ipla/software-development-platforms/client/platforms/alder-lake-desktop/12th-generation-intel-core-processors-datasheet-volume-1-of-2/007/indirect-branch-tracking/?language=en) feature starting with its 12th generation core processors, using a new instruction `endbr32` or `endbr64` added at every location the program might jump to or call into. When the CPU executes a jump/call, it asserts that the target location is a proper `endbr32` / `endbr64` instruction, before updating the program counter `PC` register to proper values. Otherwise, the CPU halts to terminate the program. This ensures that all control flows will follow the intended way, preventing ROP attacks from redirecting execution arbitrary locations. Modern OSes have already extensively leveraged `endbr32` / `endbr64` instructions. Ubuntu 24.04, for instance, has included these instructions in its packages: ``` $ objdump -d /bin/bash | head -n 50 /bin/bash: file format elf64-x86-64 Disassembly of section .init: 0000000000030000 <.init>: 30000: f3 0f 1e fa endbr64 30004: 48 83 ec 08 sub $0x8,%rsp 30008: 48 8b 05 d9 7e 12 00 mov 0x127ed9(%rip),%rax # 157ee8 <__gmon_start__@Base> 3000f: 48 85 c0 test %rax,%rax 30012: 74 02 je 30016 <unlink@plt-0xe1a> 30014: ff d0 call *%rax 30016: 48 83 c4 08 add $0x8,%rsp 3001a: c3 ret Disassembly of section .plt: 0000000000030020 <.plt>: 30020: ff 35 a2 76 12 00 push 0x1276a2(%rip) # 1576c8 <o_options@@Base+0x1cc8> 30026: ff 25 a4 76 12 00 jmp *0x1276a4(%rip) # 1576d0 <o_options@@Base+0x1cd0> 3002c: 0f 1f 40 00 nopl 0x0(%rax) 30030: f3 0f 1e fa endbr64 30034: 68 00 00 00 00 push $0x0 30039: e9 e2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3003e: 66 90 xchg %ax,%ax 30040: f3 0f 1e fa endbr64 30044: 68 01 00 00 00 push $0x1 30049: e9 d2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3004e: 66 90 xchg %ax,%ax 30050: f3 0f 1e fa endbr64 30054: 68 02 00 00 00 push $0x2 30059: e9 c2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3005e: 66 90 xchg %ax,%ax 30060: f3 0f 1e fa endbr64 30064: 68 03 00 00 00 push $0x3 30069: e9 b2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3006e: 66 90 xchg %ax,%ax 30070: f3 0f 1e fa endbr64 30074: 68 04 00 00 00 push $0x4 30079: e9 a2 ff ff ff jmp 30020 <unlink@plt-0xe10> 3007e: 66 90 xchg %ax,%ax 30080: f3 0f 1e fa endbr64 30084: 68 05 00 00 00 push $0x5 30089: e9 92 ff ff ff jmp 30020 <unlink@plt-0xe10> 3008e: 66 90 xchg %ax,%ax 30090: f3 0f 1e fa endbr64 30094: 68 06 00 00 00 push $0x6 30099: e9 82 ff ff ff jmp 30020 <unlink@plt-0xe10> 3009e: 66 90 xchg %ax,%ax ``` The `endbr32` / `endbr64` instructions has been carefully designed, so they are `nop` instructions—meaning they can do nothing at all—on CPUs prior to their introductions. Having them doesn't have any effect on older CPUs but enhances security on supported hardware. ## RISC-V’s Latest Achievements: CFI Extension The above mitigations against ROP fall into two categories: * **Compiler Modifications**: Can generate more secure binary assembly code. * **Additional CPU instructions**: Coming with Control Flow Integrity (CFI) checks to prevent exploitation Back to the beginning of designing CKB-VM, we throughly studied ROP and recognized that a vulnerability in a CKB script could potentially open the door to ROP attacks. However, we eventually did not introduce any specific mitigation against ROP in CKB-VM. Our decision was to stay aligned with the RISC-V ecosystem, avoiding shipping any custom RISC-V spec with additional instructions that would require a patched compiler. Nor do we want to maintain our own compiler set, eliminating the potential that any RISC-V-compliant compiler shall be able to produce CKB script. As the result, we shipped the first version of CKB-VM without ROP mitigations, but that does not mean we’ve ignore this issue: * We’ve [reached out](https://groups.google.com/a/groups.riscv.org/g/isa-dev/c/LyZzjJG7_18/m/pCSnKZPdBAAJ) to the RISC-V community for possible extension similar to Intel’s solution, and kept monitoring advancements in this field; * We’ve been watching over progress and writing secure CKB scripts. Since ROP relies on existing vulnerabilities, secure CKB scripts can kept ROP purely theoretical. We were thrilled when the **RISC-V CFI (Control-Flow Integrity) Extension** was officialy [ratified](https://github.com/riscv/riscv-cfi/releases/tag/v1.0) in July 2024. Designed by the brilliant minds from the RISC-V Foundation, this extension directly addresses ROP attacks with two key features: * `Zicfilp` extension introduces **landing pad**: Resembles Intel’s `endbr32` / `endbr64` to ensure that the CPU can only jump to valid, permitted targets. * `Zicfiss` extension introduces **shadow stack** with a series of instructions:. Offers a hardware solution similar to Retguard, where CPU ensures the control flow integrity or simply puts the call stack, preventing tampering throughout execution. Together, these features offer the state-of-the-art mitigations against ROP. More importantly, RISC-V CFI is now an official extension, meaning all future RISC-V CPUs, compilers, and tools will support this extension. In fact, LLVM 19 has already [supported](https://releases.llvm.org/19.1.0/docs/ReleaseNotes.html#changes-to-the-risc-v-backend), and I believe other compilers and tools will follow soon. Once fully adopted, CKB script developers can simply turn them on like a switch during code compilation. Without modifying the code, they can enjoy the security provided by RISC-V CFI extensions. Even if a vulnerability exists in a CKB script, these built-in enforcements can prevent it from being exploited. ## Final Words Security is complex. While we strive for maximum security, certain design principles might get in the way from introducing specific mitigations. ROP is a prime example: while we did learn much about it early on, implementing the best mitigations needs proper timing. Now the time has come. We are happy to introduce RISC-V CFI in CKB’s next hardfork, bringing stronger security for everyone. *** ✍🏻 Written by Xuejie Xiao His previous posts include: * [A Journey Optimizing CKB Smart Contract: Porting Bitcoin as an Example](https://blog.cryptape.com/a-journey-optimizing-ckb-smart-contract) * [Optimizing C++ Code for CKB-VM: Porting Bitcoin as an Example](https://blog.cryptape.com/optimizing-c-code-for-ckb-vm) Find more in his personal website [Less is More](https://xuejie.space/). @ 34c964ef:82a60fa4
2025-02-13 08:25:18The Bond Clean Experts: Your Ultimate Solution for End-of-Lease Cleaning Moving out of a rental property can be stressful, especially when it comes to meeting the landlord’s cleanliness expectations. That’s where The Bond Clean Experts come in! With professional experience and a commitment to excellence, we ensure your property is spotless, helping you secure your full bond refund without hassle. Why Choose The Bond Clean Experts? ✅ Experienced Professionals: Our team is trained in industry-standard cleaning techniques to deliver impeccable results.✅ Guaranteed Satisfaction: We offer a bond-back guarantee, ensuring your property meets inspection requirements.✅ Eco-Friendly Products: We use non-toxic, eco-friendly cleaning solutions to protect your health and the environment.✅ Comprehensive Cleaning Services: From kitchens and bathrooms to carpets and windows, we cover every inch of your property.✅ Affordable Pricing: Quality service at competitive rates with no hidden fees. Our Services Include: Deep Carpet Cleaning – Removing stubborn stains and odors. Kitchen & Appliance Cleaning – Ensuring spotless ovens, stovetops, and countertops. Bathroom Sanitization – Eliminating grime, mold, and bacteria. Wall & Window Cleaning – Removing marks, dust, and streaks. Floor & Tile Scrubbing – Bringing back the shine to your flooring. The Bond Cleaning Process Inspection & Quote: We assess your property’s cleaning needs and provide a transparent quote. Thorough Cleaning: Our experts deep clean every area to meet landlord expectations. Final Touches: We double-check all details and ensure nothing is overlooked. Satisfaction Guarantee: If needed, we offer a free re-clean to ensure compliance with lease requirements. Book Your Bond Clean Today! Don’t risk losing your bond due to subpar cleaning. Let The Bond Clean Experts handle the job with precision and care. 📞 Call us at 0485971499 Serving https://www.bondcleaners.au/bond-cleaning-brisbane/💬 Message us for a free quote! Make your move-out hassle-free with The Bond Clean Experts! ✨
@ 34c964ef:82a60fa4
2025-02-13 08:25:18The Bond Clean Experts: Your Ultimate Solution for End-of-Lease Cleaning Moving out of a rental property can be stressful, especially when it comes to meeting the landlord’s cleanliness expectations. That’s where The Bond Clean Experts come in! With professional experience and a commitment to excellence, we ensure your property is spotless, helping you secure your full bond refund without hassle. Why Choose The Bond Clean Experts? ✅ Experienced Professionals: Our team is trained in industry-standard cleaning techniques to deliver impeccable results.✅ Guaranteed Satisfaction: We offer a bond-back guarantee, ensuring your property meets inspection requirements.✅ Eco-Friendly Products: We use non-toxic, eco-friendly cleaning solutions to protect your health and the environment.✅ Comprehensive Cleaning Services: From kitchens and bathrooms to carpets and windows, we cover every inch of your property.✅ Affordable Pricing: Quality service at competitive rates with no hidden fees. Our Services Include: Deep Carpet Cleaning – Removing stubborn stains and odors. Kitchen & Appliance Cleaning – Ensuring spotless ovens, stovetops, and countertops. Bathroom Sanitization – Eliminating grime, mold, and bacteria. Wall & Window Cleaning – Removing marks, dust, and streaks. Floor & Tile Scrubbing – Bringing back the shine to your flooring. The Bond Cleaning Process Inspection & Quote: We assess your property’s cleaning needs and provide a transparent quote. Thorough Cleaning: Our experts deep clean every area to meet landlord expectations. Final Touches: We double-check all details and ensure nothing is overlooked. Satisfaction Guarantee: If needed, we offer a free re-clean to ensure compliance with lease requirements. Book Your Bond Clean Today! Don’t risk losing your bond due to subpar cleaning. Let The Bond Clean Experts handle the job with precision and care. 📞 Call us at 0485971499 Serving https://www.bondcleaners.au/bond-cleaning-brisbane/💬 Message us for a free quote! Make your move-out hassle-free with The Bond Clean Experts! ✨ @ f1989a96:bcaaf2c1
2025-02-06 14:01:03Good morning, readers! In India, the central bank has taken a significant step toward launching its central bank digital currency (CBDC), the digital rupee. In partnership with fintech firms Mobikwik and Cred, the digital rupee is now available to 180 million users through a new “e₹ wallet,” a CBDC wallet app designed for public use. Predictably, the CBDC comes with tight restrictions, including limits on payment amounts and frequency and extensive personal data collection, raising concerns over financial privacy. In open-source news, HRF is pleased to announce a collaboration with MIT for the 2025 MIT Bitcoin Expo. This two-day freedom-focused event will explore how Bitcoin and adjacent freedom tech can help combat financial surveillance and repression under authoritarian regimes through expert speakers, panels, workshops, and more. Elsewhere, Joltz became the first self-custodial wallet to support Taproot Assets, enabling access to stable digital dollars on a decentralized network for activists, dissidents, and others in difficult political environments. We conclude with an extensive guide from Area Bitcoin, a Brazilian education hub, thoroughly examining Brazil’s DREX CBDC and its implications for financial freedom and human rights in Brazil and beyond. **Now, let’s dive right in!** ### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **India | Central Bank Partners with Fintech Firms to Pilot Launch CBDC** The Reserve Bank of India (RBI) [partnered](https://www.businesstoday.in/personal-finance/news/story/mobikwik-cred-join-hands-with-rbi-to-fully-launch-cbdc-ers-for-android-check-features-usage-462318-2025-01-28) with fintech firms MobiKwik and Cred, alongside Yes Bank, to expand the digital rupee, India’s CBDC. With a combined user base of [180 million,](https://www.ledgerinsights.com/fintech-wallets-go-live-in-digital-rupee-cbdc-pilot/) Mobikwik and Cred will act as entry points for public access to the CBDC through their new “e₹ wallet” CBDC app. However, the app mandates video verification and imposes significant restrictions. For instance, a daily transaction cap of ₹50,000 ($577) and ₹10,000 ($115) limit per transaction. The RBI’s decision to embed the digital rupee within existing fintech firms to boost adoption leaves few avenues for financial privacy and freedom as the Indian state [pushes](https://www.lowyinstitute.org/the-interpreter/india-s-plan-world-without-cash) further towards a cashless economy. #### **El Salvador | Lawmakers Scale Back Bitcoin Legal Tender Law** El Salvador’s congress [amended](https://www.reuters.com/world/americas/lawmakers-el-salvador-rush-new-bitcoin-reform-after-imf-deal-2025-01-30/) its Bitcoin law, making private sector acceptance of Bitcoin voluntary. The reform follows a $1.4 billion loan agreement with the International Monetary Fund (IMF) that wanted to limit the government’s, citizens’, and economies’ exposure to Bitcoin. Salvadoran lawmaker Elisa Rosales [said](https://www.reuters.com/world/americas/lawmakers-el-salvador-rush-new-bitcoin-reform-after-imf-deal-2025-01-30/) the latest reform guarantees Bitcoin’s “permanence as legal tender” while facilitating its “practical implementation.” But, John Dennehy, founder of the civil society organization [Mi Primer Bitcoin](https://es.myfirstbitcoin.io/), [explained](https://x.com/jdennehy_writes/status/1885346352621617615) that the reform removed “all references of bitcoin as money or legal tender, plus the actual conditions, such as the government accepting bitcoin for things such as taxes, are now prohibited.” The future of freedom technology in El Salvador will be worth monitoring closely as the regime continues to erode protections on civil liberties. #### **Nigeria | Regime Hikes Telecom Tariffs for Citizens** In Nigeria, the regime approved a [50% increase](https://thenationonlineng.net/50-tariff-hike-a-necessary-step-or-a-burden-for-nigerians/) in telecom tariffs, further straining citizens already grappling with financial instability. Call rates will rise from 11 to 16.50 naira per minute ($0.0074 to $0.011) and SMS charges from 4 to 6 naira ($0.0026 to $0.004), exacerbating three-decade-high inflation as the ripple effects spread through the economy. Telecom companies justify the price hike as necessary for the sector’s survival amid the naira’s ongoing [devaluation](https://www.bloomberg.com/news/articles/2024-09-13/why-nigeria-s-naira-currency-ngn-usd-slumped-and-why-it-matters). [Deolu Ogunbanjo](https://www.linkedin.com/in/deolu-ogunbanjo-62b5a18b/?originalSubdomain=ng), president of the National Association of Telecoms Subscribers, however, [argues](https://thenationonlineng.net/50-tariff-hike-a-necessary-step-or-a-burden-for-nigerians/) that “this decision shows the government cares more about protecting profits than protecting people.” For Nigerians relying on mobile networks for work, banking, and daily communications, the increased costs will make phone services less accessible, putting even more pressure on civil society under an authoritarian government. #### **Nicaragua | Inter-American Court of Human Rights Rules Against Ortega** In Nicaragua, where the financial repression of individuals, opposition, and civil society is widespread, the Inter-American Court of Human Rights [ruled](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) that Daniel Ortega’s reelections since 2011 were illegitimate. This ruling “is the legal confirmation that there is no legitimate president in Nicaragua, but rather a dictator who has usurped power,” [said](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) Jaime Aparicio, a Bolivian lawyer, [adding](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) that “this is the first time that there is a legal precedent determining the illegality of Ortega’s presidency.” In a country where the regime systematically [freezes](https://www.reuters.com/world/americas/nicaragua-govt-accuses-catholic-church-money-laundering-freezes-accounts-2023-05-27/) bank accounts, seizes assets, and [shuts down](https://www.catholicnewsagency.com/news/261539/nicaraguan-dictatorship-shuts-down-more-organizations-including-dominican-nuns) nonprofits to silence dissent, this verdict sets a critical legal precedent against the abuse of state power to secure reelection. While the court lacks enforcement, its ruling strengthens legal challenges to Ortega’s rule and could provide a foundation for future actions against electoral fraud and authoritarian control. #### **Webinar Series for Nonprofits | Become Unstoppable** In an era where financial control is weaponized against dissent, the ability to transact freely is more important than ever. For activists and nonprofits operating under oppressive regimes, Bitcoin can offer a way to resist censorship, protect funds, and remain operational. Join HRF for a free, three-day webinar from March **17–19**, led by Anna Chekhovich, HRF’s Bitcoin nonprofit adoption lead and financial freedom expert at the Anti-Corruption Foundation. The sessions will run daily from **10:30 a.m. to 12:00 p.m. EDT** and are designed specifically to teach human rights defenders and nonprofit organizations how to integrate Bitcoin into their work to challenge state censorship and confiscation in a beginner-friendly way. ### [Register Here](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform) ## BITCOIN AND FREEDOM TECH NEWS #### **MIT | 2025 Bitcoin Expo** HRF is partnering with [MIT](https://www.mit.edu/) to host the [2025 MIT Bitcoin Expo](https://mitbtcexpo.org/), a two-day event from April 5-6 at the Stata Center, exploring Bitcoin and freedom technologies as tools for privacy, financial sovereignty, and civil liberties — especially for people living under authoritarian regimes. Now in its 12th year, the expo features keynotes, panels, technical workshops, and hackathons. It brings together developers, activists, students, and researchers to dive into privacy, self-sovereignty, and decentralization. Attendees will also gain hands-on experience and engage in meaningful discussions on the real-world impact of freedom technologies. Learn more about the expo and get your tickets [here](https://mitbtcexpo.org/)**.** #### **Bitcoin Mining | Two Blocks Mined by Solo Miners This Week** This week, two solo miners successfully mined Bitcoin blocks, marking a rare and significant event. The first block was [solved](https://x.com/FutureBit/status/1884740065223495821) through a collaborative effort led by the [256 Foundation](https://256foundation.org/) (where 300+ participants [pooled](https://crypto.news/solo-miner-solving-a-block-and-getting-3-146-btc/) their hashrate for a fundraising event). The second block was [mined](https://x.com/SoloSatoshi/status/1885418398345269572) independently through [solo.ckpool](https://solo.ckpool.org/) by a miner using hashrate equivalent to thousands of BitAxe devices, a type of open-source home mining hardware. The news shows that independent miners can still compete outside of large [mining pools](https://river.com/learn/terms/m/mining-pool/). These events reaffirm Bitcoin’s decentralization and censorship resistance, proving that solo mining remains viable with the proper coordination and infrastructure, which is especially key as solo mining can be done privately and quietly under tyrannical regimes. #### **Joltz Wallet | First Self-Custodial Wallet to Support Taproot Assets** Joltz has [launched](https://x.com/joltz_btc/status/1885097351108243487) the first self-custodial wallet for [Taproot Assets](https://docs.lightning.engineering/the-lightning-network/taproot-assets), enabling users to hold and transact stablecoins like USDT (Tether) directly on Bitcoin — without intermediaries. Unlike custodial solutions, Joltz ensures users retain full control over their funds while enabling BTC-to-USDT swaps through a user-friendly interface. This could expand access to stable money — particularly for activists and nonprofits in volatile markets in search of digital dollars. However, stablecoins still carry centralization and censorship risks, as issuers like Tether can freeze funds or be beholden to regulatory demands. #### **Olas | New Updates Enhance Accessibility and Features** [Olas](https://github.com/pablof7z/olas), an Instagram-like Nostr client built by [Pablof7z](https://github.com/pablof7z), [released](https://github.com/pablof7z/olas/releases/tag/0.2.0) a new update for iOS and Android. The update introduces multiple images per post, Instagram-style filters, and improved video playback. It also enhances its Nostr-native wallet functionality so users can more fluidly receive Bitcoin tips and payments. The client also made Nostr Wallet Connect (NWC), a protocol that allows apps to interact with Bitcoin Lightning wallets, more reliable for end users. Nostr clients like Olas may prove to be a useful tool for censorship-resistant communications on social networks among activists worldwide and stand as a stark contrast to centralized, permissioned alternatives. #### **OpenSats | Announces Ninth Wave of Bitcoin Grants** [OpenSats](http://opensats.org), a public nonprofit supporting open-source Bitcoin projects, [announced](https://opensats.org/blog/ninth-wave-of-bitcoin-grants) its ninth wave of Bitcoin grants advancing financial freedom and privacy. Among the recipients, [Nutstash](https://www.nutstash.app/), a multi-platform Cashu ecash wallet, enables private, censorship-resistant Bitcoin transactions — critical for human rights defenders. Another grantee, [El Tor](https://devpost.com/software/el-tor), is developing a fork of the [Tor Network](https://www.torproject.org/) integrated with Bitcoin's Lightning Network, aiming to enhance online privacy for activists and dissidents. HRF welcomes OpenSats’ continued support for decentralized tools in an increasingly surveilled world. #### **bitcoin++ | Upcoming Bitcoin Developer Conference** Bitcoin developers and freedom tech enthusiasts will [gather](https://btcplusplus.dev/conf/floripa) in Florianopolis, Brazil, from Feb. 19-22, 2025, for the special “hacking edition” [bitcoin++](https://btcplusplus.dev/) conference. Unlike past bitcoin++ events, which focused on single topics like scripting or ecash, this event will feature hands-on development to enhance Bitcoin’s privacy, scalability, and censorship resistance. Attendees will participate in workshops, live coding challenges, and technical discussions. HRF will help the event include attendees from authoritarian regimes in Latin America. Learn more about the conference or buy tickets [here](https://btcplusplus.dev/conf/floripa). ## RECOMMENDED CONTENT #### **The Risks of the DREX Central Bank Digital Currency by Area Bitcoin** In this [article](https://blog.areabitcoin.co/cbdc-drex/), [Area Bitcoin](https://www.areabitcoin.co/), a Brazilian Bitcoin education hub, examines [DREX](https://cbdctracker.hrf.org/currency/brazil), Brazil’s central bank digital currency (CBDC), and its threat to Brazilians’ financial autonomy. DREX operates as a token on a centralized, permissioned blockchain that grants officials sweeping surveillance and control over individual financial activity. Further, its strict Know-Your-Customer (KYC) and Anti-Money Laundering (AML) measures erode financial privacy. Area Bitcoin [warns](https://blog.areabitcoin.co/cbdc-drex/), “By embracing it, we risk surrendering our personal data, the fruits of our labor, and even generational wealth to political and bureaucratic oversight.” *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/)
@ f1989a96:bcaaf2c1
2025-02-06 14:01:03Good morning, readers! In India, the central bank has taken a significant step toward launching its central bank digital currency (CBDC), the digital rupee. In partnership with fintech firms Mobikwik and Cred, the digital rupee is now available to 180 million users through a new “e₹ wallet,” a CBDC wallet app designed for public use. Predictably, the CBDC comes with tight restrictions, including limits on payment amounts and frequency and extensive personal data collection, raising concerns over financial privacy. In open-source news, HRF is pleased to announce a collaboration with MIT for the 2025 MIT Bitcoin Expo. This two-day freedom-focused event will explore how Bitcoin and adjacent freedom tech can help combat financial surveillance and repression under authoritarian regimes through expert speakers, panels, workshops, and more. Elsewhere, Joltz became the first self-custodial wallet to support Taproot Assets, enabling access to stable digital dollars on a decentralized network for activists, dissidents, and others in difficult political environments. We conclude with an extensive guide from Area Bitcoin, a Brazilian education hub, thoroughly examining Brazil’s DREX CBDC and its implications for financial freedom and human rights in Brazil and beyond. **Now, let’s dive right in!** ### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **India | Central Bank Partners with Fintech Firms to Pilot Launch CBDC** The Reserve Bank of India (RBI) [partnered](https://www.businesstoday.in/personal-finance/news/story/mobikwik-cred-join-hands-with-rbi-to-fully-launch-cbdc-ers-for-android-check-features-usage-462318-2025-01-28) with fintech firms MobiKwik and Cred, alongside Yes Bank, to expand the digital rupee, India’s CBDC. With a combined user base of [180 million,](https://www.ledgerinsights.com/fintech-wallets-go-live-in-digital-rupee-cbdc-pilot/) Mobikwik and Cred will act as entry points for public access to the CBDC through their new “e₹ wallet” CBDC app. However, the app mandates video verification and imposes significant restrictions. For instance, a daily transaction cap of ₹50,000 ($577) and ₹10,000 ($115) limit per transaction. The RBI’s decision to embed the digital rupee within existing fintech firms to boost adoption leaves few avenues for financial privacy and freedom as the Indian state [pushes](https://www.lowyinstitute.org/the-interpreter/india-s-plan-world-without-cash) further towards a cashless economy. #### **El Salvador | Lawmakers Scale Back Bitcoin Legal Tender Law** El Salvador’s congress [amended](https://www.reuters.com/world/americas/lawmakers-el-salvador-rush-new-bitcoin-reform-after-imf-deal-2025-01-30/) its Bitcoin law, making private sector acceptance of Bitcoin voluntary. The reform follows a $1.4 billion loan agreement with the International Monetary Fund (IMF) that wanted to limit the government’s, citizens’, and economies’ exposure to Bitcoin. Salvadoran lawmaker Elisa Rosales [said](https://www.reuters.com/world/americas/lawmakers-el-salvador-rush-new-bitcoin-reform-after-imf-deal-2025-01-30/) the latest reform guarantees Bitcoin’s “permanence as legal tender” while facilitating its “practical implementation.” But, John Dennehy, founder of the civil society organization [Mi Primer Bitcoin](https://es.myfirstbitcoin.io/), [explained](https://x.com/jdennehy_writes/status/1885346352621617615) that the reform removed “all references of bitcoin as money or legal tender, plus the actual conditions, such as the government accepting bitcoin for things such as taxes, are now prohibited.” The future of freedom technology in El Salvador will be worth monitoring closely as the regime continues to erode protections on civil liberties. #### **Nigeria | Regime Hikes Telecom Tariffs for Citizens** In Nigeria, the regime approved a [50% increase](https://thenationonlineng.net/50-tariff-hike-a-necessary-step-or-a-burden-for-nigerians/) in telecom tariffs, further straining citizens already grappling with financial instability. Call rates will rise from 11 to 16.50 naira per minute ($0.0074 to $0.011) and SMS charges from 4 to 6 naira ($0.0026 to $0.004), exacerbating three-decade-high inflation as the ripple effects spread through the economy. Telecom companies justify the price hike as necessary for the sector’s survival amid the naira’s ongoing [devaluation](https://www.bloomberg.com/news/articles/2024-09-13/why-nigeria-s-naira-currency-ngn-usd-slumped-and-why-it-matters). [Deolu Ogunbanjo](https://www.linkedin.com/in/deolu-ogunbanjo-62b5a18b/?originalSubdomain=ng), president of the National Association of Telecoms Subscribers, however, [argues](https://thenationonlineng.net/50-tariff-hike-a-necessary-step-or-a-burden-for-nigerians/) that “this decision shows the government cares more about protecting profits than protecting people.” For Nigerians relying on mobile networks for work, banking, and daily communications, the increased costs will make phone services less accessible, putting even more pressure on civil society under an authoritarian government. #### **Nicaragua | Inter-American Court of Human Rights Rules Against Ortega** In Nicaragua, where the financial repression of individuals, opposition, and civil society is widespread, the Inter-American Court of Human Rights [ruled](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) that Daniel Ortega’s reelections since 2011 were illegitimate. This ruling “is the legal confirmation that there is no legitimate president in Nicaragua, but rather a dictator who has usurped power,” [said](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) Jaime Aparicio, a Bolivian lawyer, [adding](https://havanatimes.org/news/inter-american-human-rights-court-rules-against-nicaragua/) that “this is the first time that there is a legal precedent determining the illegality of Ortega’s presidency.” In a country where the regime systematically [freezes](https://www.reuters.com/world/americas/nicaragua-govt-accuses-catholic-church-money-laundering-freezes-accounts-2023-05-27/) bank accounts, seizes assets, and [shuts down](https://www.catholicnewsagency.com/news/261539/nicaraguan-dictatorship-shuts-down-more-organizations-including-dominican-nuns) nonprofits to silence dissent, this verdict sets a critical legal precedent against the abuse of state power to secure reelection. While the court lacks enforcement, its ruling strengthens legal challenges to Ortega’s rule and could provide a foundation for future actions against electoral fraud and authoritarian control. #### **Webinar Series for Nonprofits | Become Unstoppable** In an era where financial control is weaponized against dissent, the ability to transact freely is more important than ever. For activists and nonprofits operating under oppressive regimes, Bitcoin can offer a way to resist censorship, protect funds, and remain operational. Join HRF for a free, three-day webinar from March **17–19**, led by Anna Chekhovich, HRF’s Bitcoin nonprofit adoption lead and financial freedom expert at the Anti-Corruption Foundation. The sessions will run daily from **10:30 a.m. to 12:00 p.m. EDT** and are designed specifically to teach human rights defenders and nonprofit organizations how to integrate Bitcoin into their work to challenge state censorship and confiscation in a beginner-friendly way. ### [Register Here](https://docs.google.com/forms/d/e/1FAIpQLSf0sjqwSFQo8HGMsWIIDRyhx34TsoonOSTfYoWSy-aaBbLeSw/viewform) ## BITCOIN AND FREEDOM TECH NEWS #### **MIT | 2025 Bitcoin Expo** HRF is partnering with [MIT](https://www.mit.edu/) to host the [2025 MIT Bitcoin Expo](https://mitbtcexpo.org/), a two-day event from April 5-6 at the Stata Center, exploring Bitcoin and freedom technologies as tools for privacy, financial sovereignty, and civil liberties — especially for people living under authoritarian regimes. Now in its 12th year, the expo features keynotes, panels, technical workshops, and hackathons. It brings together developers, activists, students, and researchers to dive into privacy, self-sovereignty, and decentralization. Attendees will also gain hands-on experience and engage in meaningful discussions on the real-world impact of freedom technologies. Learn more about the expo and get your tickets [here](https://mitbtcexpo.org/)**.** #### **Bitcoin Mining | Two Blocks Mined by Solo Miners This Week** This week, two solo miners successfully mined Bitcoin blocks, marking a rare and significant event. The first block was [solved](https://x.com/FutureBit/status/1884740065223495821) through a collaborative effort led by the [256 Foundation](https://256foundation.org/) (where 300+ participants [pooled](https://crypto.news/solo-miner-solving-a-block-and-getting-3-146-btc/) their hashrate for a fundraising event). The second block was [mined](https://x.com/SoloSatoshi/status/1885418398345269572) independently through [solo.ckpool](https://solo.ckpool.org/) by a miner using hashrate equivalent to thousands of BitAxe devices, a type of open-source home mining hardware. The news shows that independent miners can still compete outside of large [mining pools](https://river.com/learn/terms/m/mining-pool/). These events reaffirm Bitcoin’s decentralization and censorship resistance, proving that solo mining remains viable with the proper coordination and infrastructure, which is especially key as solo mining can be done privately and quietly under tyrannical regimes. #### **Joltz Wallet | First Self-Custodial Wallet to Support Taproot Assets** Joltz has [launched](https://x.com/joltz_btc/status/1885097351108243487) the first self-custodial wallet for [Taproot Assets](https://docs.lightning.engineering/the-lightning-network/taproot-assets), enabling users to hold and transact stablecoins like USDT (Tether) directly on Bitcoin — without intermediaries. Unlike custodial solutions, Joltz ensures users retain full control over their funds while enabling BTC-to-USDT swaps through a user-friendly interface. This could expand access to stable money — particularly for activists and nonprofits in volatile markets in search of digital dollars. However, stablecoins still carry centralization and censorship risks, as issuers like Tether can freeze funds or be beholden to regulatory demands. #### **Olas | New Updates Enhance Accessibility and Features** [Olas](https://github.com/pablof7z/olas), an Instagram-like Nostr client built by [Pablof7z](https://github.com/pablof7z), [released](https://github.com/pablof7z/olas/releases/tag/0.2.0) a new update for iOS and Android. The update introduces multiple images per post, Instagram-style filters, and improved video playback. It also enhances its Nostr-native wallet functionality so users can more fluidly receive Bitcoin tips and payments. The client also made Nostr Wallet Connect (NWC), a protocol that allows apps to interact with Bitcoin Lightning wallets, more reliable for end users. Nostr clients like Olas may prove to be a useful tool for censorship-resistant communications on social networks among activists worldwide and stand as a stark contrast to centralized, permissioned alternatives. #### **OpenSats | Announces Ninth Wave of Bitcoin Grants** [OpenSats](http://opensats.org), a public nonprofit supporting open-source Bitcoin projects, [announced](https://opensats.org/blog/ninth-wave-of-bitcoin-grants) its ninth wave of Bitcoin grants advancing financial freedom and privacy. Among the recipients, [Nutstash](https://www.nutstash.app/), a multi-platform Cashu ecash wallet, enables private, censorship-resistant Bitcoin transactions — critical for human rights defenders. Another grantee, [El Tor](https://devpost.com/software/el-tor), is developing a fork of the [Tor Network](https://www.torproject.org/) integrated with Bitcoin's Lightning Network, aiming to enhance online privacy for activists and dissidents. HRF welcomes OpenSats’ continued support for decentralized tools in an increasingly surveilled world. #### **bitcoin++ | Upcoming Bitcoin Developer Conference** Bitcoin developers and freedom tech enthusiasts will [gather](https://btcplusplus.dev/conf/floripa) in Florianopolis, Brazil, from Feb. 19-22, 2025, for the special “hacking edition” [bitcoin++](https://btcplusplus.dev/) conference. Unlike past bitcoin++ events, which focused on single topics like scripting or ecash, this event will feature hands-on development to enhance Bitcoin’s privacy, scalability, and censorship resistance. Attendees will participate in workshops, live coding challenges, and technical discussions. HRF will help the event include attendees from authoritarian regimes in Latin America. Learn more about the conference or buy tickets [here](https://btcplusplus.dev/conf/floripa). ## RECOMMENDED CONTENT #### **The Risks of the DREX Central Bank Digital Currency by Area Bitcoin** In this [article](https://blog.areabitcoin.co/cbdc-drex/), [Area Bitcoin](https://www.areabitcoin.co/), a Brazilian Bitcoin education hub, examines [DREX](https://cbdctracker.hrf.org/currency/brazil), Brazil’s central bank digital currency (CBDC), and its threat to Brazilians’ financial autonomy. DREX operates as a token on a centralized, permissioned blockchain that grants officials sweeping surveillance and control over individual financial activity. Further, its strict Know-Your-Customer (KYC) and Anti-Money Laundering (AML) measures erode financial privacy. Area Bitcoin [warns](https://blog.areabitcoin.co/cbdc-drex/), “By embracing it, we risk surrendering our personal data, the fruits of our labor, and even generational wealth to political and bureaucratic oversight.” *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/) @ 04ed2b8f:75be6756
2025-02-13 08:02:39Freedom. It’s the word on everyone’s lips, the dream of every soul. We long for it, we chase it, we believe that if we can break free from this chain or that constraint, we will finally be free. **But true freedom is not about external circumstances—it’s about control.** The truth is, **the most powerful chains are the ones we place on ourselves**. The world can throw its challenges at you, life can dish out its unfair blows, but **if you cannot control yourself, your thoughts, your emotions, your reactions, then you are no different than a prisoner.** There is no freedom in chaos. There is no freedom in losing control. **Freedom is mastery—mastery of the self.** ## **Freedom Begins Within** You can have all the money in the world, live in the most luxurious place, and have every material possession your heart desires, but **if you cannot control your impulses, your habits, your desires—none of that will matter.** You are still a slave to your cravings. You are still a puppet to your own emotions, and that is **no real freedom.** What does freedom look like? - **It’s the power to act with purpose, not to react out of emotion.** - **It’s the strength to stay disciplined when every part of you wants to quit.** - **It’s the courage to say ‘no’ to distractions, to temptation, to things that steer you off course.** - **It’s the clarity to make choices that serve your growth, not your immediate desires.** True freedom is the ability to say, “I am in control of myself. I do not let my circumstances control me, nor my emotions rule me. I dictate my actions, my thoughts, my destiny.” ## **Self-Control: The Ultimate Weapon** The power to control yourself is your greatest weapon. Without it, **you are at the mercy of every challenge, every temptation, and every fleeting emotion**. You may feel like you are “free,” but without self-discipline, you are just a puppet swaying in the wind, vulnerable to every whim that blows your way. - **The impulse to procrastinate? You overcome it.** - **The desire to give up? You push through it.** - **The craving for comfort? You choose growth.** In the face of any storm, a man with self-control remains grounded, focused, and clear. He doesn’t react in anger or fear—he acts with purpose, with precision, and with vision. A man who cannot control himself is a man who is owned by his emotions, his desires, his distractions. But the man who conquers his mind, his body, his impulses—he is the one who **owns his life.** ## **The Price of Freedom** It’s not easy to control yourself. It requires constant effort, relentless discipline, and the courage to face yourself head-on. It means saying ‘no’ to what feels good now, to invest in what will make you stronger later. It means constantly improving, constantly fighting the urge to quit, to give in, to indulge in comfort. But the price of freedom is worth it. **For when you have control over yourself, no one can take your power.** You become the master of your fate. **You become unshakable.** ## **Freedom Through Discipline** So, ask yourself: **Are you truly free, or are you simply a slave to your impulses?** - **Do you control your actions, or do your actions control you?** - **Are you the master of your emotions, or are they the masters of you?** Freedom isn’t just about having no chains; it’s about not letting anything control you—least of all yourself. **And when you control yourself, there’s nothing you can’t accomplish.** A man who cannot control himself is never truly free. But a man who conquers his mind, his habits, his emotions—he is unstoppable. **Now go and choose to control yourself, and unlock the freedom that’s waiting for you. Or remain a prisoner to your impulses, forever shackled by the chains of your own making. The choice is yours.**
@ 04ed2b8f:75be6756
2025-02-13 08:02:39Freedom. It’s the word on everyone’s lips, the dream of every soul. We long for it, we chase it, we believe that if we can break free from this chain or that constraint, we will finally be free. **But true freedom is not about external circumstances—it’s about control.** The truth is, **the most powerful chains are the ones we place on ourselves**. The world can throw its challenges at you, life can dish out its unfair blows, but **if you cannot control yourself, your thoughts, your emotions, your reactions, then you are no different than a prisoner.** There is no freedom in chaos. There is no freedom in losing control. **Freedom is mastery—mastery of the self.** ## **Freedom Begins Within** You can have all the money in the world, live in the most luxurious place, and have every material possession your heart desires, but **if you cannot control your impulses, your habits, your desires—none of that will matter.** You are still a slave to your cravings. You are still a puppet to your own emotions, and that is **no real freedom.** What does freedom look like? - **It’s the power to act with purpose, not to react out of emotion.** - **It’s the strength to stay disciplined when every part of you wants to quit.** - **It’s the courage to say ‘no’ to distractions, to temptation, to things that steer you off course.** - **It’s the clarity to make choices that serve your growth, not your immediate desires.** True freedom is the ability to say, “I am in control of myself. I do not let my circumstances control me, nor my emotions rule me. I dictate my actions, my thoughts, my destiny.” ## **Self-Control: The Ultimate Weapon** The power to control yourself is your greatest weapon. Without it, **you are at the mercy of every challenge, every temptation, and every fleeting emotion**. You may feel like you are “free,” but without self-discipline, you are just a puppet swaying in the wind, vulnerable to every whim that blows your way. - **The impulse to procrastinate? You overcome it.** - **The desire to give up? You push through it.** - **The craving for comfort? You choose growth.** In the face of any storm, a man with self-control remains grounded, focused, and clear. He doesn’t react in anger or fear—he acts with purpose, with precision, and with vision. A man who cannot control himself is a man who is owned by his emotions, his desires, his distractions. But the man who conquers his mind, his body, his impulses—he is the one who **owns his life.** ## **The Price of Freedom** It’s not easy to control yourself. It requires constant effort, relentless discipline, and the courage to face yourself head-on. It means saying ‘no’ to what feels good now, to invest in what will make you stronger later. It means constantly improving, constantly fighting the urge to quit, to give in, to indulge in comfort. But the price of freedom is worth it. **For when you have control over yourself, no one can take your power.** You become the master of your fate. **You become unshakable.** ## **Freedom Through Discipline** So, ask yourself: **Are you truly free, or are you simply a slave to your impulses?** - **Do you control your actions, or do your actions control you?** - **Are you the master of your emotions, or are they the masters of you?** Freedom isn’t just about having no chains; it’s about not letting anything control you—least of all yourself. **And when you control yourself, there’s nothing you can’t accomplish.** A man who cannot control himself is never truly free. But a man who conquers his mind, his habits, his emotions—he is unstoppable. **Now go and choose to control yourself, and unlock the freedom that’s waiting for you. Or remain a prisoner to your impulses, forever shackled by the chains of your own making. The choice is yours.** @ bf47c19e:c3d2573b
2025-02-13 07:56:50Originalni tekst na [dvadesetjedan.com](https://dvadesetjedan.com/blog/niko-ne-moze-zabraniti-bitcoin) ###### Autor: [Parker Lewis](https://x.com/parkeralewis) / Prevod na srpski: [Plumsky](https://t.me/Plumski) --- Ideja da država može nekako zabraniti bitcoin je jedna od poslednjih faza tuge, tačno pred prihvatanje realnosti. Posledica ove rečenice je priznanje da bitcoin “funkcioniše”. U stvari, ona predstavlja činjenicu da bitcoin funkcioniše toliko dobro da on preti postojećim državnim monopolima nad novcem i da će zbog toga države da ga unište kroz regulativne prepreke da bi eliminisale tu pretnju. Gledajte na tvrdnju da će države zabraniti bitcoin kao kondicionalnu logiku. Da li bitcoin funkcioniše kao novac? Ako je odgovor „ne“, onda države nemaju šta da zabrane. Ako je odgovor „da“, onda će države da probaju da ga zabrane. Znači, glavna poenta ovog razmišljanja je pretpostavka da bitcoin funkcioiniše kao novac. Onda je sledeće logično pitanje da li intervencija od strane države može uspešno da uništi upravo taj funkcionalan bitcoin. 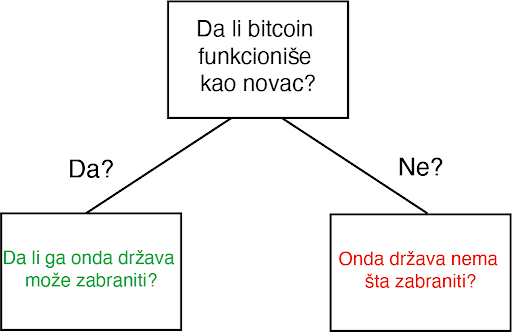 Za početak, svako ko pokušava da razume kako, zašto, ili da li bitcoin funkcioniše mora da proceni ta pitanja potpuno nezavisno od prouzrekovanja državne regulacije ili intervencije. Iako je nesumnjivo da bitcoin mora da postoji uzgred državnih regulativa, zamislite na momenat da države ne postoje. Sam od sebe, da li bi bitcoin funkcionisao kao novac, kad bi se prepustio slobodnom tržištu? Ovo pitanje se širi u dodatna pitanja i ubrzo se pretvara u bunar bez dna. Šta je novac? Šta su svojstva koja čine jednu vrstu novca bolje od druge? Da li bitcoin poseduje ta svojstva? Da li je bitcoin bolja verzija novca po takvim osobinama? Ako je finalni zaključak da bitcoin ne funkcioniše kao novac, implikacije državne intervencije su nebitne. Ali, ako je bitcoin funkcionalan kao novac, ta pitanja onda postaju bitna u ovoj debati, i svako ko o tome razmišlja bi morao imati taj početnički kontekst da bi mogao proceniti da li je uopšte moguće zabraniti. Po svom dizajnu, bitcoin postoji van države. Ali bitcoin nije samo van kontrole države, on u stvari funkcioniše bez bilo kakve saradnje centralizovanih identiteta. On je globalan i decentralizovan. Svako može pristupiti bitcoinu bez potrebe saglasnosti bilo koga i što se više širi sve je teže cenzurisati celokupnu mrežu. Arhitektura bitcoina je namerno izmišljena da bude otporna na bilo koje pokušaje države da ga zabrane. Ovo ne znači da države širom sveta neće pokušavati da ga regulišu, oporezuju ili čak da potpuno zabrane njegovo korišćenje. Naravno da će biti puno bitki i otpora protiv usvajanja bitcoina među građanima. Federal Reserve i Američki Treasury (i njihovi globalni suparnici) se neće ležeći predati dok bitcoin sve više i više ugrožava njihove monopole prihvatljivog novca. Doduše, pre nego što se odbaci ideja da države mogu potpuno zabraniti bitcoin, mora se prvo razumeti posledice tog stava i njegovog glasnika. #### Progresija poricanja i stepeni tuge Pripovesti skeptičara se neprestano menjaju kroz vreme. Prvi stepen tuge: bitcoin nikad ne može funkcionisati-njegova vrednost je osnovana ni na čemu. On je moderna verzija tulip manije. Sa svakim ciklusom uzbuđenja, vrednost bitcoina skače i onda vrlo brzo se vraća na dole. Često nazvano kao kraj njegove vrednosti, bitcoin svaki put odbija da umre i njegova vrednost pronađe nivo koji je uvek viši od prethodnih ciklusa globalne usvajanja. Tulip pripovetka postaje stara i dosadna i skeptičari pređu na više nijansirane teme, i time menjaju bazu debate. Drugi stepen tuge predstoji: bitcoin je manjkav kao novac. On je previše volatilan da bi bio valuta, ili je suviše spor da bi se koristio kao sistem plaćanja, ili se ne može proširiti dovoljno da zadovolji sve promete plaćanja na svetu, ili troši isuviše struje. Taj niz kritike ide sve dalje i dalje. Ovaj drugi stepen je progresija poricanja i dosta je udaljen od ideje da je bitcoin ništa više od bukvalno bezvrednog ničega. Uprkos tim pretpostavnim manjcima, vrednost bitcoin mreže nastavje da raste vremenom. Svaki put, ona ne umire, nasuprot, ona postaje sve veća i jača. Dok se skeptičari bave ukazivanjem na manjke, bitcoin ne prestaje. Rast u vrednosti je prouzrokovan jednostavnom dinamikom tržišta: postoji više kupca nego prodavca. To je sve i to je razlog rasta u adopciji. Sve više i više ljudi shvata zašto postoji fundamentalna potražnja za bitcoinom i zašto/kako on funkcioniše. To je razlog njegovog dugotrajnog rasta. Dokle god ga sve više ljudi koristi za čuvanje vrednosti, neće pasti cena snabdevanja. Zauvek će postojati samo 21 milion bitcoina. Nebitno je koliko ljudi zahtevaju bitcoin, njegova cela količina je uvek ista i neelastična. Dok skeptičari nastavljaju sa svojom starom pričom, mase ljudi nastavljaju da eliminišu zabludu i zahtevaju bitcoin zbog njegovih prednosti u smislu novčanih svojstva. Između ostalog, ne postoji grupa ljudi koja je više upoznata sa svim argumentima protiv bitcoina od samih bitcoinera.  Očajanje počinje da se stvara i onda se debata još jedanput pomera. Sada nije više činjenica je vrednost bitcoina osnovana ni na čemu niti da ima manjke kao valuta; sada se debata centrira na regulaciji državnih autoriteta. U ovom zadnjem stepenu tuge, bitcoin se predstavlja kao u stvari isuviše uspešnom alatkom i zbog toga države ne smeju dozvoliti da on postoji. Zaista? Znači da je genijalnost čoveka ponovo ostvarila funkcionalan novac u tehnološko superiornoj formi, čije su posledice zaista neshvatljive, i da će države upravo taj izum nekako zabraniti. Primetite da tom izjavom skeptičari praktično priznaju svoj poraz. Ovo su poslednji pokušaji u seriji promašenih argumenata. Skeptičari u isto vreme prihvataju da postoji fundamentalna potražnja za bitcoinom a onda se premeštaju na neosnovan stav da ga države mogu zabraniti. Ajde da se poigramo i tim pitanjem. Kada bih zapravo razvijene države nastupile na scenu i pokušale da zabrane bitcoin? Trenutno, Federal Reserve i Treasury ne smatraju bitcoin kao ozbiljnu pretnju superiornosti dolara. Po njihovom celokupnom mišljenju, bitcoin je slatka mala igračka i ne može da funkcioniše kao novac. Sadašnja kompletna kupovna moć bitcoina je manja od $200 milijardi. Sa druge strane, zlato ima celokupnu vrednost od $8 triliona (40X veću od bitcoina) i količina odštampanog novca (M2) je otprilike 15 triliona (75X veličine bitcoinove vrednosti). Kada će Federal Reserve i Treasury da počne da smatra bitcoin kao ozbiljnu pretnju? Kad bitcoin poraste na $1, $2 ili $3 triliona? Možete i sami da izaberete nivo, ali implikacija je da će bitcoin biti mnogo vredniji, i posedovaće ga sve više ljudi širom sveta, pre nego što će ga državne vlasti shvatiti kao obiljnog protivnika. Predsednik Tramp & Treasury Sekretar Mnučin o Bitcoinu (2019): > „Ja neću pričati o bitcoinu za 10 godina, u to možete biti sigurni {…} Ja bi se kladio da čak za 5 ili 6 godina neću više pričati o bitcoinu kao sekretar Trusury-a. Imaću preča posla {…} Mogu vam obećati da ja lično neću biti pun bitcoina.“ – Sekretar Treasury-a Stiv Mnučin > „Ja nisam ljubitelj bitcoina {…}, koji nije novac i čija vrednost je jako volatilna i osnovana na praznom vazduhu.“ – Predsednik Donald J. Tramp Znači, logika skeptika ide ovako: bitcoin ne funkcioniše, ali ako funkcioniše, onda će ga država zabraniti. Ali, države slobodnog sveta neće pokušati da ga zabrane dokle god se on ne pokaže kao ozbiljna pretnja. U tom trenutku, bitcoin će biti vredniji i sigurno teži da se zabrani, pošto će ga više ljudi posedovati na mnogo širem geografskom prostoru. Ignorišite fundamentalne činjenice i asimetriju koja je urođena u globalnom dešavanju monetizacije zato što u slučaju da ste u pravu, države će taj proces zabraniti. Na kojoj strani tog argumenta bi radije stajao racionalan ekonomski učesnik? Posedovanje finansijske imovine kojoj vrednost toliko raste da preti globalnoj rezervnoj valuti, ili nasuprot – nemati tu imovinu? Sa pretpostavkom da individualci razumeju zašto je mogućnost (a sve više i verovatnoća) ove realnosti, koji stav je logičniji u ovom scenariju? Asimetrija dve strane ovog argumenta sama od sebe zahteva da je prvi stav onaj istinit i da fundamentalno razumevanje potražnje bitcoina samo još više ojačava to mišljenje. #### Niko ne moze zabraniti bitcoin Razmislite šta bitcoin u stvari predstavlja pa onda šta bi predstavljala njegova zabrana. Bitcoin je konverzija subjektivne vrednosti, stvorena i razmenjena u realnošću, u digitalne potpise. Jednostavno rečeno, to je konverzija ljudskog vremena u novac. Kad neko zahteva bitcoin, oni u isto vreme ne zahtevaju neki drugi posed, nek to bio dolar, kuća, auto ili hrana itd. Bitcoin predstavlja novčanu štednju koja sa sobom žrtvuje druge imovine i servise. Zabrana bitcoina bi bio napad na najosnovnije ljudske slobode koje je on upravo stvoren da brani. Zamislite reakciju svih onih koji su prihvatili bitcoin: „Bilo je zabavno, alatka za koju su svi eksperti tvrdili da neće nikad funkcionisati, sada toliko dobro radi i sad ti isti eksperti i autoriteti kažu da mi to nemožemo koristiti. Svi idite kući, predstava je gotova.“verovanje da će svi ljudi koji su učestvovali u bitcoin usvajanju, suverenitetu koji nudi i finansiskoj slobodi, odjednom samo da se predaju osnovnom rušenju njihovih prava je potpuno iracionalna pozicija. > Novac je jedan od najbitnijih instrumenata za slobodu koji je ikad izmišljen. Novac je to što u postojećem društvu ostvaruje mogućnosti siromašnom čoveku – čiji je domet veći nego onaj koji je bio dostižan bogatim ljudima pre ne toliko puno generacija.“ – F. A. Hajek Države nisu uspele da zabrane konzumiranje alkohola, droga, kupovinu vatrenog oružja, pa ni posedovanje zlata. Država može samo pomalo da uspori pristup ili da deklariše posedovanje ilegalnim, ali ne može da uništi nešto što veliki broj raznovrsnih ljudi smatra vrednim. Kada je SAD zabranila privatno posedovanje zlata 1933., zlato nije palo u vrednosti ili nestalo sa finansijskog tržišta. Ono je u stvari poraslo u vrednosti u poređenju sa dolarom, i samo trideset godina kasnije, zabrana je bila ukinuta. Ne samo da bitcoin nudi veću vrednosno obećanje od bilo kog drugog dobra koje su države pokušale da zabrane (uključujući i zlato); nego po svojim osobinama, njega je mnogo teže zabraniti. Bitcoin je globalan i decentralizovan. On ne poštuje granice i osiguran je mnoštvom nodova i kriptografskim potpisima. Sam postupak zabrane bi zahtevao da se u isto vreme zaustavi „open source“ softver koji emituje i izvršava slanje i potvrđivanje digitalno enkriptovanih ključeva i potpisa. Ta zabrana bi morala biti koordinisana između velikog broja zemalja, sa tim da je nemoguće znati gde se ti nodovi i softver nalazi ili da se zaustavi instaliranje novih nodova u drugim pravnim nadležnostima. Da ne pominjemo i ustavske pitanja, bilo bi tehnički neizvodljivo da se takva zabrana primeni na bilo kakav značajan način. 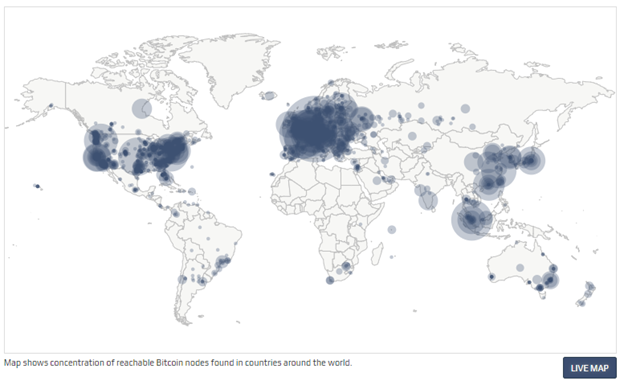 Čak kada bih sve zemlje iz G-20 grupe koordinisale takvu zabranu u isto vreme, to ne bi uništilo bitcoin. U stvari, to bi bilo samoubistvo za fiat novčani sistem. To bi još više prikazalo masama da je bitcoin u stvari novac koji treba shvatiti ozbiljno, i to bi samo od sebe započelo globalnu igru vatanje mačke za rep. Bitcoin nema centralnu tačku za napad; bitcoin rudari, nodovi i digitalni potpisi su rasejani po celom svetu. Svaki aspekt bitcoina je decentralizovan, zato su glavni stubovi njegove arhitekture da učesnici uvek treba kontrolisati svoje potpise i upravljati svojim nodom. Što više digitalnih potpisa i nodova koji postoje, to je više bitcoin decentralizovan, i to je više odbranjiva njegova mreža od strane neprijatelja. Što je više zemalja gde rudari izvršavaju svoj posao, to je manji rizik da jedan nadležni identitet može uticati na njegov bezbednosni sistem. Koordinisan internacionalni napad na bitcoin bi samo koristio da bitcoin još više ojača svoj imuni sistem. Na kraju krajeva, to bi ubrzalo seobu iz tradicionalnog finansijskog sistema (i njegovih valuta) a i inovaciju koja postoji u bitcoin ekosistemu. Sa svakom bivšom pretnjom, bitcoin je maštovito pronalazio način da ih neutrališe pa i koordinisan napad od strane država ne bi bio ništa drugačiji. 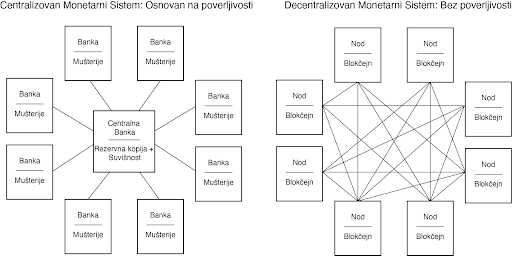 Inovacija u ovoj oblasti koja se odlikuje svojom „permissionless“ (bez dozvole centralnih identiteta) osobinom, omogućava odbranu od svakojakih napada. Sve varijante napada koje su bile predvidjene je upravo to što zahteva konstantnu inovaciju bitcoina. To je ona Adam Smitova nevidljiva ruka, ali dopingovana. Pojedinačni učesnici mogu da veruju da su motivisani nekim većim uzrokom, ali u stvari, korisnost kaja je ugrađena u bitcoin stvara kod učesnika dovoljno snažan podsticaj da omogući svoje preživljavanje. Sopstveni interes milione, ako ne milijarde, nekoordinisanih ljudi koji se jedino slažu u svojom međusobnom potrebom za funkcionalnim novcem podstiče inovacije u bitcoinu. Danas, možda to izgleda kao neka kul nova tehnologija ili neki dobar investment u finansijskom portfoliju, ali čak i ako to mnogi ne razumeju, bitcoin je apsolutna nužnost u svetu. To je tako zato što je novac nužnost a historijski priznate valute se fundamentalno raspadaju. Pre dva meseca, tržište američkih državnih obveznica je doživeo kolaps na šta je Federal Reserve reagovao time što je povećao celokupnu količinu dolara u postojanju za $250 milijardi, a još više u bliskoj budućnosti. Tačno ovo je razlog zašto je bitcoin nužnost a ne samo luksuzni dodatak. Kada inovacija omogućava bazično funkcionisanje ekonomije ne postoji ni jedna država na svetu koja može da zaustavi njenu adopciju i rast. Novac je nužnost a bitcoin znatno poboljšava sistem novca koji je ikada postojao pre njega. Sa više praktične strane, pokušaj zabranjivanja bitcoina ili njegove velike regulacije od nadležnosti bi direktno bilo u korist susedne nadležnih organa. Podsticaj da se odustane od koordinisanog napada na bitcoin bi bio isuviše veliki da bi takvi dogovori bili uspešni. Kada bi SAD deklarisovale posed bitcoina ilegalnim sutra, da li bi to zaustavilo njegov rast, razvoj i adopciji i da li bi to smanjilo vrednost celokupne mreže? Verovatno. Da li bi to uništilo bitcoin? Ne bi. Bitcoin predstavlja najpokretljivije kapitalno sredstvo na svetu. Zemlje i nadležne strukture koje kreiraju regulativnu strukturu koja najmanje ustručava korišćenje bitcoina će biti dobitnici velike količine uliva kapitala u svoje države. #### Zabrana Bitcoinove Zatvoreničke Dileme 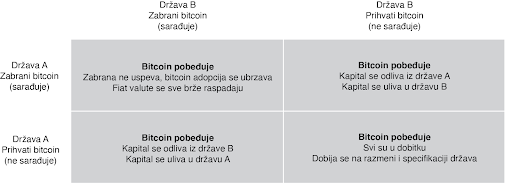 U praksi, zatvorenička dilema nije igra jedan na jedan. Ona je multidimenzijska i uključuje mnoštvo nadležnosti, čiji se interesi nadmeću međusobno, i to uskraćuje mogućnosti bilo kakve mogućnosti zabrane. Ljudski kapital, fizički kapital i novčani kapital će sav ići u pravcu država i nadležnosti koje najmanje ustručuju bitcoin. To se možda neće desiti sve odjednom, ali pokušaji zabrane su isto za badava koliko bi bilo odseći sebi nos u inat svom licu. To ne znači da države to neće pokušati. India je već probala da zabrani bitcoin. Kina je uvela puno restrikcija. Drugi će da prate njihove tragove. Ali svaki put kada država preduzme takve korake, to ima nepredvidljive efekte povećanja bitcoin adopcije. Pokušaji zabranjivanja bitcoina su jako efektivne marketing kampanje. Bitcoin postoji kao sistem nevezan za jednu suverenu državu i kao novac je otporan na cenzuru. On je dizajniran da postoji van državne kontrole. Pokušaji da se taj koncept zabrani samo još više daje njemu razlog i logiku za postojanje. #### Jedini Pobednički Potez je da se Uključiš u Igru Zabrana bitcoina je trošenje vremena. Neki će to pokušati; ali svi će biti neuspešni. Sami ti pokušaji će još više ubrzati njegovu adopciju i širenje. Biće to vetar od 100 km/h koji raspaljuje vatru. To će ojačati bitcoin sve više i doprineće njegovoj pouzdanosti. U svakom slučaju, verovanje da će države zabraniti bitcoin u momentu kada on postane dovoljno velika pretnja rezervnim valutam sveta, je iracionalan razlog da se on no poseduje kao instrument štednje novca. To ne samo da podrazumeva da je bitcoin novac, ali u isto vreme i ignoriše glavne razloge zašto je to tako: on je decentralizovan i otporan na cenzure. Zamislite da razumete jednu od nojvećih tajni današnjice i da u isto vreme tu tajnu asimetrije koju bitcoin nudi ne primenjujete u svoju korist zbog straha od države. Pre će biti, neko ko razume zašto bitcoin funkcioniše i da ga država ne može zaustaviti, ili nepuno znanje postoji u razumevanju kako bitcoin uopšte funckioniše. Počnite sa razmatranjem fundamentalnih pitanja, a onda primenite to kao temelj da bi procenili bilo koji potencijalan rizik od strane budućih regulacija ili restrikcija državnih organa. I nikad nemojte da zaboravite na vrednost asimetrije između dve strane ovde prezentiranih argumenata. Jedini pobednički potez je da se uključite u igru. Stavovi ovde prezentirani su samo moji i ne predstavljaju Unchained Capital ili moje kolege. Zahvaljujem se Fil Gajgeru za razmatranje teksta i primedbe. [Originalni tekst](https://unchained.com/blog/bitcoin-cannot-be-banned/)
@ bf47c19e:c3d2573b
2025-02-13 07:56:50Originalni tekst na [dvadesetjedan.com](https://dvadesetjedan.com/blog/niko-ne-moze-zabraniti-bitcoin) ###### Autor: [Parker Lewis](https://x.com/parkeralewis) / Prevod na srpski: [Plumsky](https://t.me/Plumski) --- Ideja da država može nekako zabraniti bitcoin je jedna od poslednjih faza tuge, tačno pred prihvatanje realnosti. Posledica ove rečenice je priznanje da bitcoin “funkcioniše”. U stvari, ona predstavlja činjenicu da bitcoin funkcioniše toliko dobro da on preti postojećim državnim monopolima nad novcem i da će zbog toga države da ga unište kroz regulativne prepreke da bi eliminisale tu pretnju. Gledajte na tvrdnju da će države zabraniti bitcoin kao kondicionalnu logiku. Da li bitcoin funkcioniše kao novac? Ako je odgovor „ne“, onda države nemaju šta da zabrane. Ako je odgovor „da“, onda će države da probaju da ga zabrane. Znači, glavna poenta ovog razmišljanja je pretpostavka da bitcoin funkcioiniše kao novac. Onda je sledeće logično pitanje da li intervencija od strane države može uspešno da uništi upravo taj funkcionalan bitcoin. 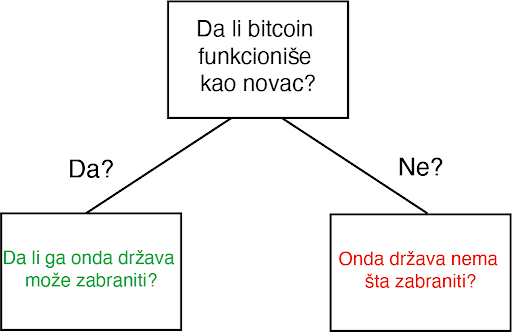 Za početak, svako ko pokušava da razume kako, zašto, ili da li bitcoin funkcioniše mora da proceni ta pitanja potpuno nezavisno od prouzrekovanja državne regulacije ili intervencije. Iako je nesumnjivo da bitcoin mora da postoji uzgred državnih regulativa, zamislite na momenat da države ne postoje. Sam od sebe, da li bi bitcoin funkcionisao kao novac, kad bi se prepustio slobodnom tržištu? Ovo pitanje se širi u dodatna pitanja i ubrzo se pretvara u bunar bez dna. Šta je novac? Šta su svojstva koja čine jednu vrstu novca bolje od druge? Da li bitcoin poseduje ta svojstva? Da li je bitcoin bolja verzija novca po takvim osobinama? Ako je finalni zaključak da bitcoin ne funkcioniše kao novac, implikacije državne intervencije su nebitne. Ali, ako je bitcoin funkcionalan kao novac, ta pitanja onda postaju bitna u ovoj debati, i svako ko o tome razmišlja bi morao imati taj početnički kontekst da bi mogao proceniti da li je uopšte moguće zabraniti. Po svom dizajnu, bitcoin postoji van države. Ali bitcoin nije samo van kontrole države, on u stvari funkcioniše bez bilo kakve saradnje centralizovanih identiteta. On je globalan i decentralizovan. Svako može pristupiti bitcoinu bez potrebe saglasnosti bilo koga i što se više širi sve je teže cenzurisati celokupnu mrežu. Arhitektura bitcoina je namerno izmišljena da bude otporna na bilo koje pokušaje države da ga zabrane. Ovo ne znači da države širom sveta neće pokušavati da ga regulišu, oporezuju ili čak da potpuno zabrane njegovo korišćenje. Naravno da će biti puno bitki i otpora protiv usvajanja bitcoina među građanima. Federal Reserve i Američki Treasury (i njihovi globalni suparnici) se neće ležeći predati dok bitcoin sve više i više ugrožava njihove monopole prihvatljivog novca. Doduše, pre nego što se odbaci ideja da države mogu potpuno zabraniti bitcoin, mora se prvo razumeti posledice tog stava i njegovog glasnika. #### Progresija poricanja i stepeni tuge Pripovesti skeptičara se neprestano menjaju kroz vreme. Prvi stepen tuge: bitcoin nikad ne može funkcionisati-njegova vrednost je osnovana ni na čemu. On je moderna verzija tulip manije. Sa svakim ciklusom uzbuđenja, vrednost bitcoina skače i onda vrlo brzo se vraća na dole. Često nazvano kao kraj njegove vrednosti, bitcoin svaki put odbija da umre i njegova vrednost pronađe nivo koji je uvek viši od prethodnih ciklusa globalne usvajanja. Tulip pripovetka postaje stara i dosadna i skeptičari pređu na više nijansirane teme, i time menjaju bazu debate. Drugi stepen tuge predstoji: bitcoin je manjkav kao novac. On je previše volatilan da bi bio valuta, ili je suviše spor da bi se koristio kao sistem plaćanja, ili se ne može proširiti dovoljno da zadovolji sve promete plaćanja na svetu, ili troši isuviše struje. Taj niz kritike ide sve dalje i dalje. Ovaj drugi stepen je progresija poricanja i dosta je udaljen od ideje da je bitcoin ništa više od bukvalno bezvrednog ničega. Uprkos tim pretpostavnim manjcima, vrednost bitcoin mreže nastavje da raste vremenom. Svaki put, ona ne umire, nasuprot, ona postaje sve veća i jača. Dok se skeptičari bave ukazivanjem na manjke, bitcoin ne prestaje. Rast u vrednosti je prouzrokovan jednostavnom dinamikom tržišta: postoji više kupca nego prodavca. To je sve i to je razlog rasta u adopciji. Sve više i više ljudi shvata zašto postoji fundamentalna potražnja za bitcoinom i zašto/kako on funkcioniše. To je razlog njegovog dugotrajnog rasta. Dokle god ga sve više ljudi koristi za čuvanje vrednosti, neće pasti cena snabdevanja. Zauvek će postojati samo 21 milion bitcoina. Nebitno je koliko ljudi zahtevaju bitcoin, njegova cela količina je uvek ista i neelastična. Dok skeptičari nastavljaju sa svojom starom pričom, mase ljudi nastavljaju da eliminišu zabludu i zahtevaju bitcoin zbog njegovih prednosti u smislu novčanih svojstva. Između ostalog, ne postoji grupa ljudi koja je više upoznata sa svim argumentima protiv bitcoina od samih bitcoinera.  Očajanje počinje da se stvara i onda se debata još jedanput pomera. Sada nije više činjenica je vrednost bitcoina osnovana ni na čemu niti da ima manjke kao valuta; sada se debata centrira na regulaciji državnih autoriteta. U ovom zadnjem stepenu tuge, bitcoin se predstavlja kao u stvari isuviše uspešnom alatkom i zbog toga države ne smeju dozvoliti da on postoji. Zaista? Znači da je genijalnost čoveka ponovo ostvarila funkcionalan novac u tehnološko superiornoj formi, čije su posledice zaista neshvatljive, i da će države upravo taj izum nekako zabraniti. Primetite da tom izjavom skeptičari praktično priznaju svoj poraz. Ovo su poslednji pokušaji u seriji promašenih argumenata. Skeptičari u isto vreme prihvataju da postoji fundamentalna potražnja za bitcoinom a onda se premeštaju na neosnovan stav da ga države mogu zabraniti. Ajde da se poigramo i tim pitanjem. Kada bih zapravo razvijene države nastupile na scenu i pokušale da zabrane bitcoin? Trenutno, Federal Reserve i Treasury ne smatraju bitcoin kao ozbiljnu pretnju superiornosti dolara. Po njihovom celokupnom mišljenju, bitcoin je slatka mala igračka i ne može da funkcioniše kao novac. Sadašnja kompletna kupovna moć bitcoina je manja od $200 milijardi. Sa druge strane, zlato ima celokupnu vrednost od $8 triliona (40X veću od bitcoina) i količina odštampanog novca (M2) je otprilike 15 triliona (75X veličine bitcoinove vrednosti). Kada će Federal Reserve i Treasury da počne da smatra bitcoin kao ozbiljnu pretnju? Kad bitcoin poraste na $1, $2 ili $3 triliona? Možete i sami da izaberete nivo, ali implikacija je da će bitcoin biti mnogo vredniji, i posedovaće ga sve više ljudi širom sveta, pre nego što će ga državne vlasti shvatiti kao obiljnog protivnika. Predsednik Tramp & Treasury Sekretar Mnučin o Bitcoinu (2019): > „Ja neću pričati o bitcoinu za 10 godina, u to možete biti sigurni {…} Ja bi se kladio da čak za 5 ili 6 godina neću više pričati o bitcoinu kao sekretar Trusury-a. Imaću preča posla {…} Mogu vam obećati da ja lično neću biti pun bitcoina.“ – Sekretar Treasury-a Stiv Mnučin > „Ja nisam ljubitelj bitcoina {…}, koji nije novac i čija vrednost je jako volatilna i osnovana na praznom vazduhu.“ – Predsednik Donald J. Tramp Znači, logika skeptika ide ovako: bitcoin ne funkcioniše, ali ako funkcioniše, onda će ga država zabraniti. Ali, države slobodnog sveta neće pokušati da ga zabrane dokle god se on ne pokaže kao ozbiljna pretnja. U tom trenutku, bitcoin će biti vredniji i sigurno teži da se zabrani, pošto će ga više ljudi posedovati na mnogo širem geografskom prostoru. Ignorišite fundamentalne činjenice i asimetriju koja je urođena u globalnom dešavanju monetizacije zato što u slučaju da ste u pravu, države će taj proces zabraniti. Na kojoj strani tog argumenta bi radije stajao racionalan ekonomski učesnik? Posedovanje finansijske imovine kojoj vrednost toliko raste da preti globalnoj rezervnoj valuti, ili nasuprot – nemati tu imovinu? Sa pretpostavkom da individualci razumeju zašto je mogućnost (a sve više i verovatnoća) ove realnosti, koji stav je logičniji u ovom scenariju? Asimetrija dve strane ovog argumenta sama od sebe zahteva da je prvi stav onaj istinit i da fundamentalno razumevanje potražnje bitcoina samo još više ojačava to mišljenje. #### Niko ne moze zabraniti bitcoin Razmislite šta bitcoin u stvari predstavlja pa onda šta bi predstavljala njegova zabrana. Bitcoin je konverzija subjektivne vrednosti, stvorena i razmenjena u realnošću, u digitalne potpise. Jednostavno rečeno, to je konverzija ljudskog vremena u novac. Kad neko zahteva bitcoin, oni u isto vreme ne zahtevaju neki drugi posed, nek to bio dolar, kuća, auto ili hrana itd. Bitcoin predstavlja novčanu štednju koja sa sobom žrtvuje druge imovine i servise. Zabrana bitcoina bi bio napad na najosnovnije ljudske slobode koje je on upravo stvoren da brani. Zamislite reakciju svih onih koji su prihvatili bitcoin: „Bilo je zabavno, alatka za koju su svi eksperti tvrdili da neće nikad funkcionisati, sada toliko dobro radi i sad ti isti eksperti i autoriteti kažu da mi to nemožemo koristiti. Svi idite kući, predstava je gotova.“verovanje da će svi ljudi koji su učestvovali u bitcoin usvajanju, suverenitetu koji nudi i finansiskoj slobodi, odjednom samo da se predaju osnovnom rušenju njihovih prava je potpuno iracionalna pozicija. > Novac je jedan od najbitnijih instrumenata za slobodu koji je ikad izmišljen. Novac je to što u postojećem društvu ostvaruje mogućnosti siromašnom čoveku – čiji je domet veći nego onaj koji je bio dostižan bogatim ljudima pre ne toliko puno generacija.“ – F. A. Hajek Države nisu uspele da zabrane konzumiranje alkohola, droga, kupovinu vatrenog oružja, pa ni posedovanje zlata. Država može samo pomalo da uspori pristup ili da deklariše posedovanje ilegalnim, ali ne može da uništi nešto što veliki broj raznovrsnih ljudi smatra vrednim. Kada je SAD zabranila privatno posedovanje zlata 1933., zlato nije palo u vrednosti ili nestalo sa finansijskog tržišta. Ono je u stvari poraslo u vrednosti u poređenju sa dolarom, i samo trideset godina kasnije, zabrana je bila ukinuta. Ne samo da bitcoin nudi veću vrednosno obećanje od bilo kog drugog dobra koje su države pokušale da zabrane (uključujući i zlato); nego po svojim osobinama, njega je mnogo teže zabraniti. Bitcoin je globalan i decentralizovan. On ne poštuje granice i osiguran je mnoštvom nodova i kriptografskim potpisima. Sam postupak zabrane bi zahtevao da se u isto vreme zaustavi „open source“ softver koji emituje i izvršava slanje i potvrđivanje digitalno enkriptovanih ključeva i potpisa. Ta zabrana bi morala biti koordinisana između velikog broja zemalja, sa tim da je nemoguće znati gde se ti nodovi i softver nalazi ili da se zaustavi instaliranje novih nodova u drugim pravnim nadležnostima. Da ne pominjemo i ustavske pitanja, bilo bi tehnički neizvodljivo da se takva zabrana primeni na bilo kakav značajan način. 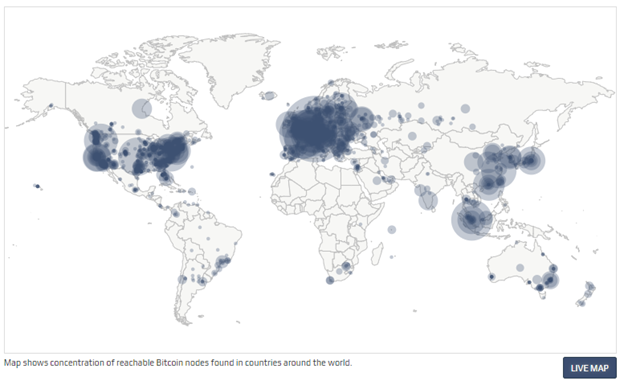 Čak kada bih sve zemlje iz G-20 grupe koordinisale takvu zabranu u isto vreme, to ne bi uništilo bitcoin. U stvari, to bi bilo samoubistvo za fiat novčani sistem. To bi još više prikazalo masama da je bitcoin u stvari novac koji treba shvatiti ozbiljno, i to bi samo od sebe započelo globalnu igru vatanje mačke za rep. Bitcoin nema centralnu tačku za napad; bitcoin rudari, nodovi i digitalni potpisi su rasejani po celom svetu. Svaki aspekt bitcoina je decentralizovan, zato su glavni stubovi njegove arhitekture da učesnici uvek treba kontrolisati svoje potpise i upravljati svojim nodom. Što više digitalnih potpisa i nodova koji postoje, to je više bitcoin decentralizovan, i to je više odbranjiva njegova mreža od strane neprijatelja. Što je više zemalja gde rudari izvršavaju svoj posao, to je manji rizik da jedan nadležni identitet može uticati na njegov bezbednosni sistem. Koordinisan internacionalni napad na bitcoin bi samo koristio da bitcoin još više ojača svoj imuni sistem. Na kraju krajeva, to bi ubrzalo seobu iz tradicionalnog finansijskog sistema (i njegovih valuta) a i inovaciju koja postoji u bitcoin ekosistemu. Sa svakom bivšom pretnjom, bitcoin je maštovito pronalazio način da ih neutrališe pa i koordinisan napad od strane država ne bi bio ništa drugačiji. 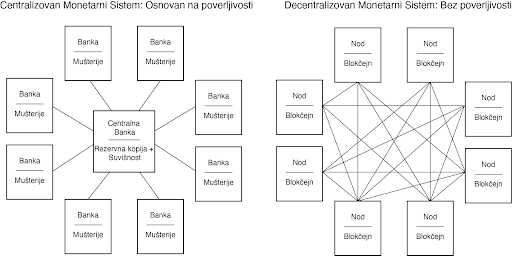 Inovacija u ovoj oblasti koja se odlikuje svojom „permissionless“ (bez dozvole centralnih identiteta) osobinom, omogućava odbranu od svakojakih napada. Sve varijante napada koje su bile predvidjene je upravo to što zahteva konstantnu inovaciju bitcoina. To je ona Adam Smitova nevidljiva ruka, ali dopingovana. Pojedinačni učesnici mogu da veruju da su motivisani nekim većim uzrokom, ali u stvari, korisnost kaja je ugrađena u bitcoin stvara kod učesnika dovoljno snažan podsticaj da omogući svoje preživljavanje. Sopstveni interes milione, ako ne milijarde, nekoordinisanih ljudi koji se jedino slažu u svojom međusobnom potrebom za funkcionalnim novcem podstiče inovacije u bitcoinu. Danas, možda to izgleda kao neka kul nova tehnologija ili neki dobar investment u finansijskom portfoliju, ali čak i ako to mnogi ne razumeju, bitcoin je apsolutna nužnost u svetu. To je tako zato što je novac nužnost a historijski priznate valute se fundamentalno raspadaju. Pre dva meseca, tržište američkih državnih obveznica je doživeo kolaps na šta je Federal Reserve reagovao time što je povećao celokupnu količinu dolara u postojanju za $250 milijardi, a još više u bliskoj budućnosti. Tačno ovo je razlog zašto je bitcoin nužnost a ne samo luksuzni dodatak. Kada inovacija omogućava bazično funkcionisanje ekonomije ne postoji ni jedna država na svetu koja može da zaustavi njenu adopciju i rast. Novac je nužnost a bitcoin znatno poboljšava sistem novca koji je ikada postojao pre njega. Sa više praktične strane, pokušaj zabranjivanja bitcoina ili njegove velike regulacije od nadležnosti bi direktno bilo u korist susedne nadležnih organa. Podsticaj da se odustane od koordinisanog napada na bitcoin bi bio isuviše veliki da bi takvi dogovori bili uspešni. Kada bi SAD deklarisovale posed bitcoina ilegalnim sutra, da li bi to zaustavilo njegov rast, razvoj i adopciji i da li bi to smanjilo vrednost celokupne mreže? Verovatno. Da li bi to uništilo bitcoin? Ne bi. Bitcoin predstavlja najpokretljivije kapitalno sredstvo na svetu. Zemlje i nadležne strukture koje kreiraju regulativnu strukturu koja najmanje ustručava korišćenje bitcoina će biti dobitnici velike količine uliva kapitala u svoje države. #### Zabrana Bitcoinove Zatvoreničke Dileme 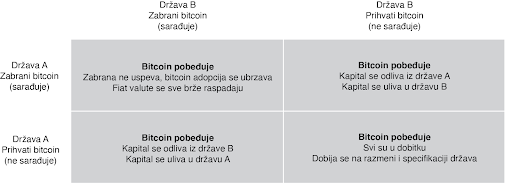 U praksi, zatvorenička dilema nije igra jedan na jedan. Ona je multidimenzijska i uključuje mnoštvo nadležnosti, čiji se interesi nadmeću međusobno, i to uskraćuje mogućnosti bilo kakve mogućnosti zabrane. Ljudski kapital, fizički kapital i novčani kapital će sav ići u pravcu država i nadležnosti koje najmanje ustručuju bitcoin. To se možda neće desiti sve odjednom, ali pokušaji zabrane su isto za badava koliko bi bilo odseći sebi nos u inat svom licu. To ne znači da države to neće pokušati. India je već probala da zabrani bitcoin. Kina je uvela puno restrikcija. Drugi će da prate njihove tragove. Ali svaki put kada država preduzme takve korake, to ima nepredvidljive efekte povećanja bitcoin adopcije. Pokušaji zabranjivanja bitcoina su jako efektivne marketing kampanje. Bitcoin postoji kao sistem nevezan za jednu suverenu državu i kao novac je otporan na cenzuru. On je dizajniran da postoji van državne kontrole. Pokušaji da se taj koncept zabrani samo još više daje njemu razlog i logiku za postojanje. #### Jedini Pobednički Potez je da se Uključiš u Igru Zabrana bitcoina je trošenje vremena. Neki će to pokušati; ali svi će biti neuspešni. Sami ti pokušaji će još više ubrzati njegovu adopciju i širenje. Biće to vetar od 100 km/h koji raspaljuje vatru. To će ojačati bitcoin sve više i doprineće njegovoj pouzdanosti. U svakom slučaju, verovanje da će države zabraniti bitcoin u momentu kada on postane dovoljno velika pretnja rezervnim valutam sveta, je iracionalan razlog da se on no poseduje kao instrument štednje novca. To ne samo da podrazumeva da je bitcoin novac, ali u isto vreme i ignoriše glavne razloge zašto je to tako: on je decentralizovan i otporan na cenzure. Zamislite da razumete jednu od nojvećih tajni današnjice i da u isto vreme tu tajnu asimetrije koju bitcoin nudi ne primenjujete u svoju korist zbog straha od države. Pre će biti, neko ko razume zašto bitcoin funkcioniše i da ga država ne može zaustaviti, ili nepuno znanje postoji u razumevanju kako bitcoin uopšte funckioniše. Počnite sa razmatranjem fundamentalnih pitanja, a onda primenite to kao temelj da bi procenili bilo koji potencijalan rizik od strane budućih regulacija ili restrikcija državnih organa. I nikad nemojte da zaboravite na vrednost asimetrije između dve strane ovde prezentiranih argumenata. Jedini pobednički potez je da se uključite u igru. Stavovi ovde prezentirani su samo moji i ne predstavljaju Unchained Capital ili moje kolege. Zahvaljujem se Fil Gajgeru za razmatranje teksta i primedbe. [Originalni tekst](https://unchained.com/blog/bitcoin-cannot-be-banned/) @ ec42c765:328c0600
2025-02-05 22:53:03てすと nostr:nevent1qqst3uqlls4yr9vys4dza2sgjle3ly37trck7jgdmtr23uuz52usjrqqqnjgr nostr:nevent1qqsdvchy5d27zt3z05rr3q6vvmzgslslxwu0p4dfkvxwhmvxldn9djguvagp2 test
@ ec42c765:328c0600
2025-02-05 22:53:03てすと nostr:nevent1qqst3uqlls4yr9vys4dza2sgjle3ly37trck7jgdmtr23uuz52usjrqqqnjgr nostr:nevent1qqsdvchy5d27zt3z05rr3q6vvmzgslslxwu0p4dfkvxwhmvxldn9djguvagp2 test @ 8d5ba92c:c6c3ecd5
2025-02-05 22:06:18**There I was, minding my own business at the airport (i.e., arranging the list of Bitcoin/Freedom podcasts for the next seven hours of flight), when I came across a scene that could have been ripped straight from a show about the decline of civilization. Heart-wrenching. Shocking. Dystopian. To put it simply, what the f*ck?!** ## Prologue. A family of five, including two early-school kids (let’s call them 'Timmy' and 'Amy', around 5 and 7 years old), a father who looked like he’d given up on life, and a perfect mother multitasking like a pro—breastfeeding a baby while chowing down on a Big Mac. Oh yeah, the whole family was happily consuming their McDonald’s junk as if it was their daily ritual. Watching little kids eat that stuff? A mix of anger and sadness. But seeing a breastfeeding mother give her newborn absolute garbage? The scene I can’t forget. She also washed it all down with some fizzy, sugary, chemical-laden sludge later on. Still, while breastfeeding. Because, you know, nothing screams nourishment like a steady diet of artificial stuff. Best to get them hooked in the first few months, right? ## Act One: The Mother’s Masterpiece. A modern-day Madonna, cradling her infant while balancing junk food’s finest. The baby, blissfully unaware of the nutritional betrayal unfolding in real-time, probably wasn’t even dreaming of normal food that might one day help it grow into a healthy being. Seeing this scene, knowing all the options available at the airport—many much more reasonable than this crap—and watching the family enjoy their 'sacred food', I’m almost certain this little one had been getting a side of heavily processed rubbish long before it even left the womb... Rave: A standing ovation for conscious parenting. ## Act Two: Innocent Contribution. Just when I thought the scene couldn’t get worse, little “Timmy” decided to play bartender. With the enthusiasm of a child clearly raised on a steady diet of Big Macs and Coca-Cola (or whatever other delicacies were on offer), he extended his cup to his tiny brother or sister. The devoted mother, of course, helped him guide the straw to the baby’s mouth. *“Drink, little one! Drink not just from my body, but directly from the cup. Drink this (crap) with us!”* Why not? If McDonald’s was good enough for everyone in the family, surely it was good enough for the baby sibling, right? They all looked almost proud of Timmy’s little “sharing is caring” moment. Meanwhile, my heart shattered into a million pieces, each one screaming, *“Seriously?! Should I interfere? How would they react?”* I was close enough to keep taking photos, staring at them with my mouth probably hanging open, horror written all over my face. The mother met my gaze once—cold, unreadable. No 'leave us alone.' No 'it’s our business.' No 'what's wrong, tell us.' Just... nothing. My husband, noticing my growing frustration and sensing I was about to step in, whispered, *“Let it go. You won’t save them in 10 minutes at the airport.”* Maybe he was right. But I’ll be thinking about it for a long time… ## Act Three: A Recipe for Regret. It was as if the parents had collectively agreed that their bodies were nothing more than human garbage bins, and their children were just smaller versions of the same. Let’s be clear: adults can do whatever they want with their health. If you want to treat your body like a landfill, go ahead—it’s your funeral (literally). But when you drag your kids into it, it’s no longer a personal choice. It’s more like a crime. These children didn’t sign up for a life of artificial flavors, empty calories, and a future riddled with health problems. They deserve better. And if you’re reading this thinking, *‘What’s the big deal?’*—let's talk. My brain is on the verge of exploding, trying to understand how anyone could actively contribute to the slow, painful destruction of the people they (presumably) love. You should love and respect your own body, and even more so the lives of your kids. What could possibly justify feeding your family McDonald's if it’s not the very last option you have on earth to survive? Please, help me understand why! ## Epilogue: The Aftertaste. As I stepped into the boarding line, I couldn’t shake the thought: Is this really where we are now? A world where care and nutritional awareness no longer exist. Where junk food became a family tradition. Where children are raised on a cocktail of chemicals when better options are right there! **To the McDonald’s family at the airport—and anyone on their way to becoming one: Not sure if you enjoyed your meal. If you did, I wish you luck. You’ll need it.** https://i.nostr.build/e8f3h9iuDNQbtmaF.png **And please, maybe—just maybe—consider giving your kids a chance. They deserve more than a trash life packed with chemicals in a paper bag.** ---- BTC Your Mind. Let it ₿eat. Şelale
@ 8d5ba92c:c6c3ecd5
2025-02-05 22:06:18**There I was, minding my own business at the airport (i.e., arranging the list of Bitcoin/Freedom podcasts for the next seven hours of flight), when I came across a scene that could have been ripped straight from a show about the decline of civilization. Heart-wrenching. Shocking. Dystopian. To put it simply, what the f*ck?!** ## Prologue. A family of five, including two early-school kids (let’s call them 'Timmy' and 'Amy', around 5 and 7 years old), a father who looked like he’d given up on life, and a perfect mother multitasking like a pro—breastfeeding a baby while chowing down on a Big Mac. Oh yeah, the whole family was happily consuming their McDonald’s junk as if it was their daily ritual. Watching little kids eat that stuff? A mix of anger and sadness. But seeing a breastfeeding mother give her newborn absolute garbage? The scene I can’t forget. She also washed it all down with some fizzy, sugary, chemical-laden sludge later on. Still, while breastfeeding. Because, you know, nothing screams nourishment like a steady diet of artificial stuff. Best to get them hooked in the first few months, right? ## Act One: The Mother’s Masterpiece. A modern-day Madonna, cradling her infant while balancing junk food’s finest. The baby, blissfully unaware of the nutritional betrayal unfolding in real-time, probably wasn’t even dreaming of normal food that might one day help it grow into a healthy being. Seeing this scene, knowing all the options available at the airport—many much more reasonable than this crap—and watching the family enjoy their 'sacred food', I’m almost certain this little one had been getting a side of heavily processed rubbish long before it even left the womb... Rave: A standing ovation for conscious parenting. ## Act Two: Innocent Contribution. Just when I thought the scene couldn’t get worse, little “Timmy” decided to play bartender. With the enthusiasm of a child clearly raised on a steady diet of Big Macs and Coca-Cola (or whatever other delicacies were on offer), he extended his cup to his tiny brother or sister. The devoted mother, of course, helped him guide the straw to the baby’s mouth. *“Drink, little one! Drink not just from my body, but directly from the cup. Drink this (crap) with us!”* Why not? If McDonald’s was good enough for everyone in the family, surely it was good enough for the baby sibling, right? They all looked almost proud of Timmy’s little “sharing is caring” moment. Meanwhile, my heart shattered into a million pieces, each one screaming, *“Seriously?! Should I interfere? How would they react?”* I was close enough to keep taking photos, staring at them with my mouth probably hanging open, horror written all over my face. The mother met my gaze once—cold, unreadable. No 'leave us alone.' No 'it’s our business.' No 'what's wrong, tell us.' Just... nothing. My husband, noticing my growing frustration and sensing I was about to step in, whispered, *“Let it go. You won’t save them in 10 minutes at the airport.”* Maybe he was right. But I’ll be thinking about it for a long time… ## Act Three: A Recipe for Regret. It was as if the parents had collectively agreed that their bodies were nothing more than human garbage bins, and their children were just smaller versions of the same. Let’s be clear: adults can do whatever they want with their health. If you want to treat your body like a landfill, go ahead—it’s your funeral (literally). But when you drag your kids into it, it’s no longer a personal choice. It’s more like a crime. These children didn’t sign up for a life of artificial flavors, empty calories, and a future riddled with health problems. They deserve better. And if you’re reading this thinking, *‘What’s the big deal?’*—let's talk. My brain is on the verge of exploding, trying to understand how anyone could actively contribute to the slow, painful destruction of the people they (presumably) love. You should love and respect your own body, and even more so the lives of your kids. What could possibly justify feeding your family McDonald's if it’s not the very last option you have on earth to survive? Please, help me understand why! ## Epilogue: The Aftertaste. As I stepped into the boarding line, I couldn’t shake the thought: Is this really where we are now? A world where care and nutritional awareness no longer exist. Where junk food became a family tradition. Where children are raised on a cocktail of chemicals when better options are right there! **To the McDonald’s family at the airport—and anyone on their way to becoming one: Not sure if you enjoyed your meal. If you did, I wish you luck. You’ll need it.** https://i.nostr.build/e8f3h9iuDNQbtmaF.png **And please, maybe—just maybe—consider giving your kids a chance. They deserve more than a trash life packed with chemicals in a paper bag.** ---- BTC Your Mind. Let it ₿eat. Şelale @ 91bea5cd:1df4451c
2025-02-04 17:15:57### Definição de ULID: Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível. #### Gerar ULID ```sql CREATE EXTENSION IF NOT EXISTS pgcrypto; CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000'; output TEXT = ''; unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER); -- 10 entropy bytes ulid = timestamp || gen_random_bytes(10); -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ``` #### ULID TO UUID ```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF; v = regexp_split_to_array(ulid, ''); -- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]); -- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]); RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE; CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### UUID to ULID ```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### Gera 11 Digitos aleatórios: YBKXG0CKTH4 ```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT; -- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars; END; $$ LANGUAGE plpgsql; ``` #### Exemplo de USO ```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL ); -- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ``` ### Fontes - https://github.com/scoville/pgsql-ulid - https://github.com/geckoboard/pgulid
@ 91bea5cd:1df4451c
2025-02-04 17:15:57### Definição de ULID: Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível. #### Gerar ULID ```sql CREATE EXTENSION IF NOT EXISTS pgcrypto; CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\\000\\000\\000\\000\\000\\000'; output TEXT = ''; unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER); -- 10 entropy bytes ulid = timestamp || gen_random_bytes(10); -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ``` #### ULID TO UUID ```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF; v = regexp_split_to_array(ulid, ''); -- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]); -- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]); RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE; CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### UUID to ULID ```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN -- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31))); -- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31))); RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ``` #### Gera 11 Digitos aleatórios: YBKXG0CKTH4 ```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT; -- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars; END; $$ LANGUAGE plpgsql; ``` #### Exemplo de USO ```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL ); -- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ``` ### Fontes - https://github.com/scoville/pgsql-ulid - https://github.com/geckoboard/pgulid @ da0b9bc3:4e30a4a9
2025-02-13 06:36:12Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/884478
@ da0b9bc3:4e30a4a9
2025-02-13 06:36:12Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/884478 @ fd208ee8:0fd927c1
2025-02-02 10:33:19# GitCitadel Development Operations We, at GitCitadel, have been updating, moving, and rearranging our servers, for quite some time. As a rather large, complex, sprawling project, we have the infrastructure setup to match, so we've decided to give you all a quick run-down of what we are doing behind-the-scenes. ## Supplier Coordination 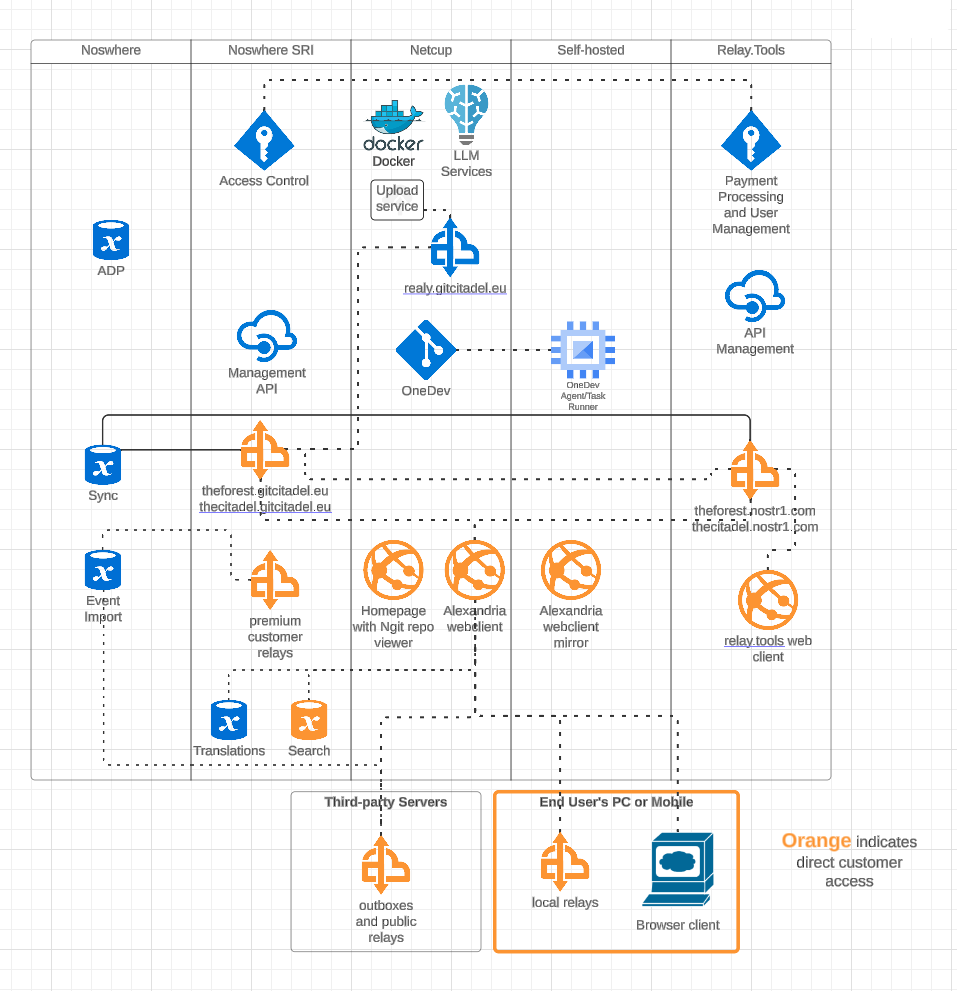 Our first task, this week, was figuring out who would host what where. We have four different locations, where our infra is stored and managed, including two locations from our suppliers. We got that straightened out, quickly, and it's all slowly coming together and being connected and networked. Exciting to watch our DevOps landscape evolve and all of the knowledge-transfer that the interactions provide. ## OneDev Implementation 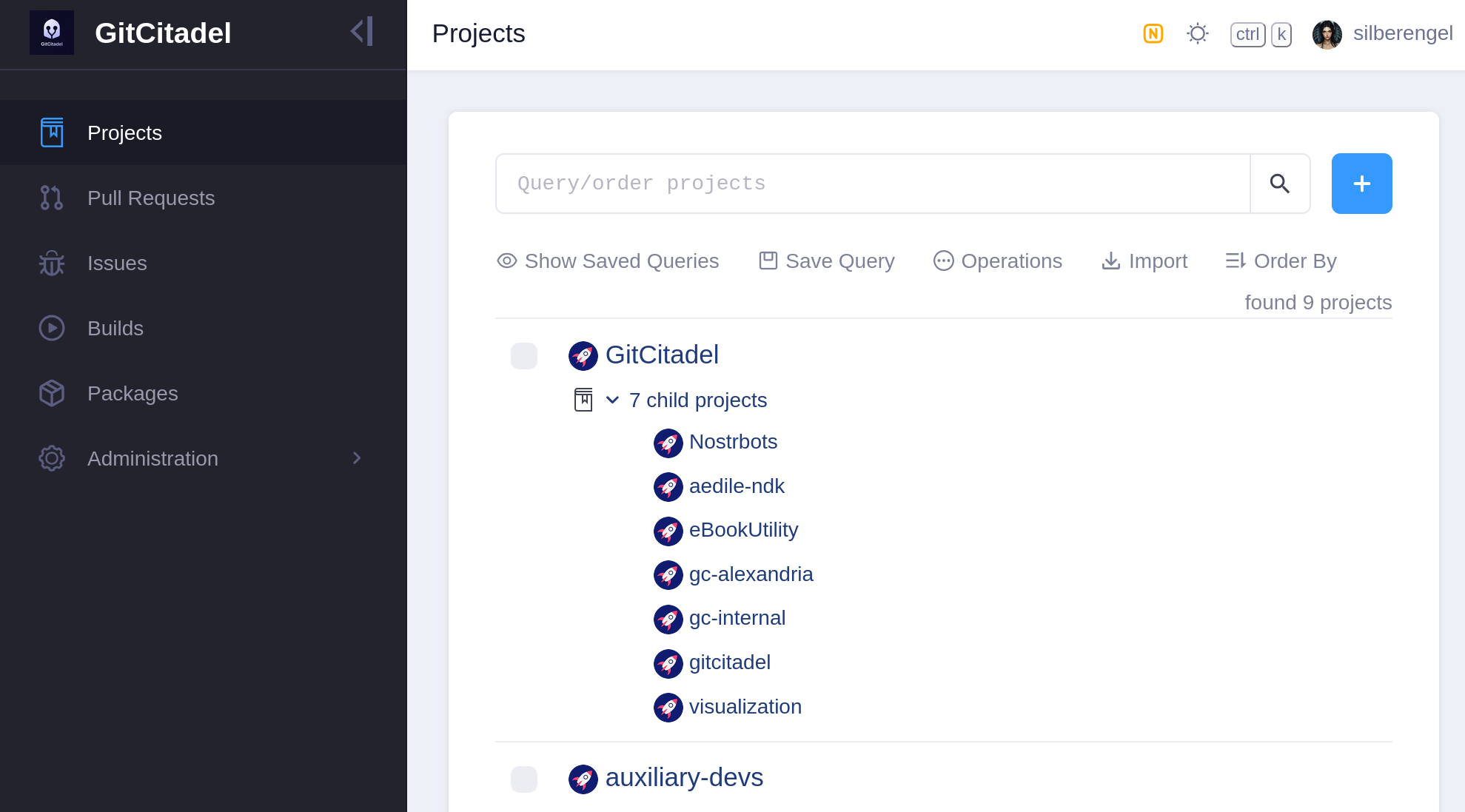 Our biggest internal infra project this week was the migration of all of our issues from Jira, build scripts from Jenkins, and repos from GitHub to a [self-hosted OneDev instance](https://onedev.gitcitadel.eu). In the future, all of our internal build, test, issue, patch/PR, etc. effort will take place there. We also have a separate repo there for communicating with external developers and suppliers. Our [team's GitHub projects](https://github.com/ShadowySupercode) will be demoted to mirrors and a place for external devs to PR to. Public issues and patches will continue to be managed over our self-hosted [GitWorkshop instance](nostr:naddr1qvzqqqrhnypzplfq3m5v3u5r0q9f255fdeyz8nyac6lagssx8zy4wugxjs8ajf7pqy88wumn8ghj7mn0wvhxcmmv9uqq5emfw33kjarpv3jkcs83wav). We're especially glad to finally escape the GitHub Gulag, and avoid being bled dry by Jira fees, without having to give up the important features that we've come to know and love. So, yay! ## Next Infrasteps ### Automated Testing Now, that we have everything tied up in one, neat, backed-up package, we can finally move on to the nitty-gritty and the dirty work. So, we're rolling up our sleeves and writing the Selenium smoke test for our [Alexandria client](https://next-alexandria.gitcitadel.eu). We'll be running that in Docker containers containing different "typical Nostr" images, such as Chrome browser with Nostr Connect signing extension, or Firefox browser with Nos2x-fox extension. Once we get the Nsec Bunker and Amber logins going, we'll add test cases and images for them, as well. (Yes, we can do Bunker. I hope you are in awe at our powers). We are also designing an automated infrastructure test, that will simply rattle through all the various internal and external websites and relays, to make sure that everything is still online and responsive. After that, a Gherkin-based [Behave feature test](https://behave.readthedocs.io/en/latest/) for Alexandria is planned, so that we can prevent regression of completed functionality, from one release to the next. The Gherkin scenarios are written and attached to our stories before development begins (we use acceptance tests as requirements), a manual test-execution is then completed, in order to set the story to *Done*. These completed scenarios will be automated, following each release, with the resulting script linked to from the origin story. 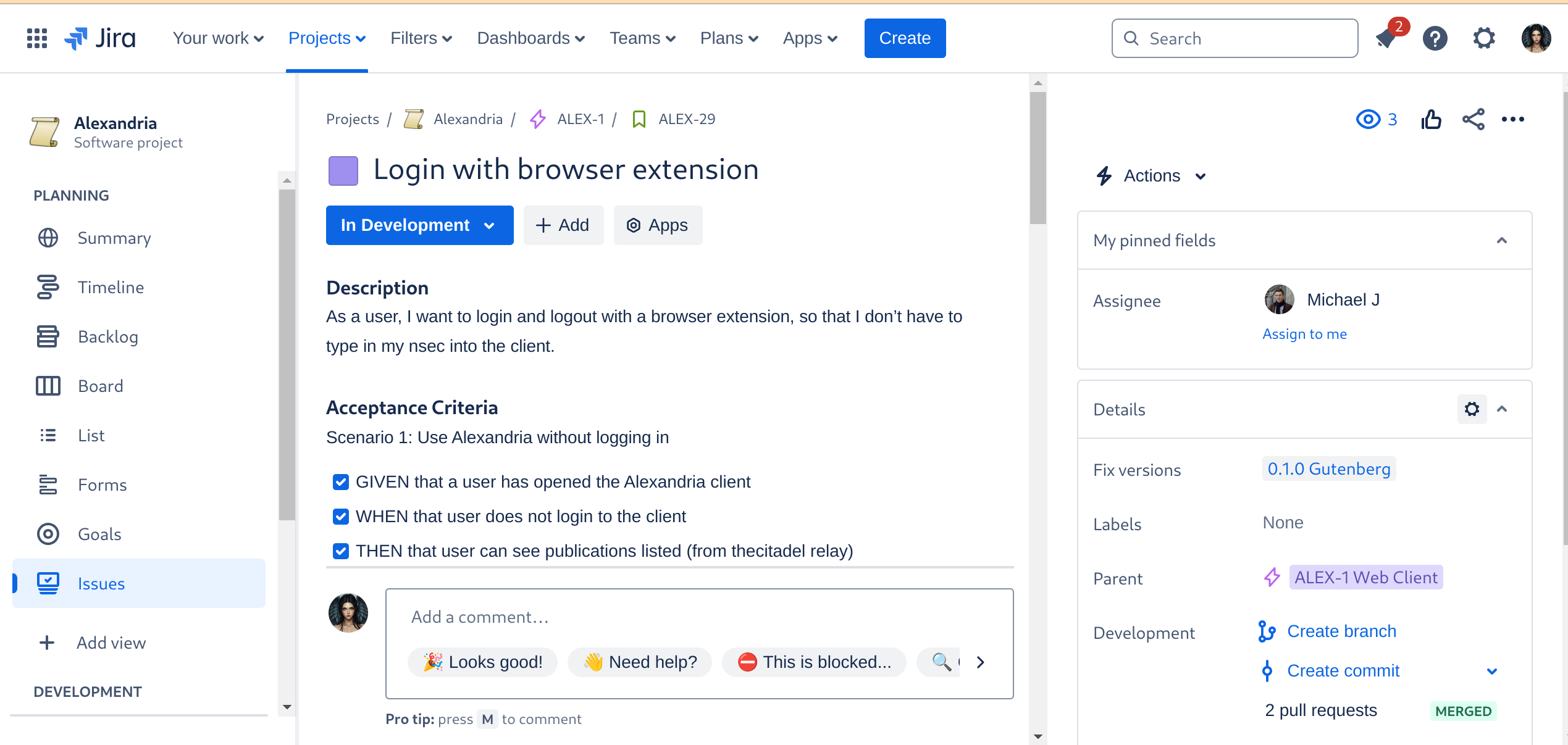 ### Automated Builds As the crowning glory of every DevOps tool chain stands the build automation. This is where everything gets tied together, straightened out, configured, tested, measured, and -- if everything passes the quality gates -- released. I don't have to tell you how much time developers spend staring at the build process display, praying that it all goes through and they can celebrate a Green Wave. 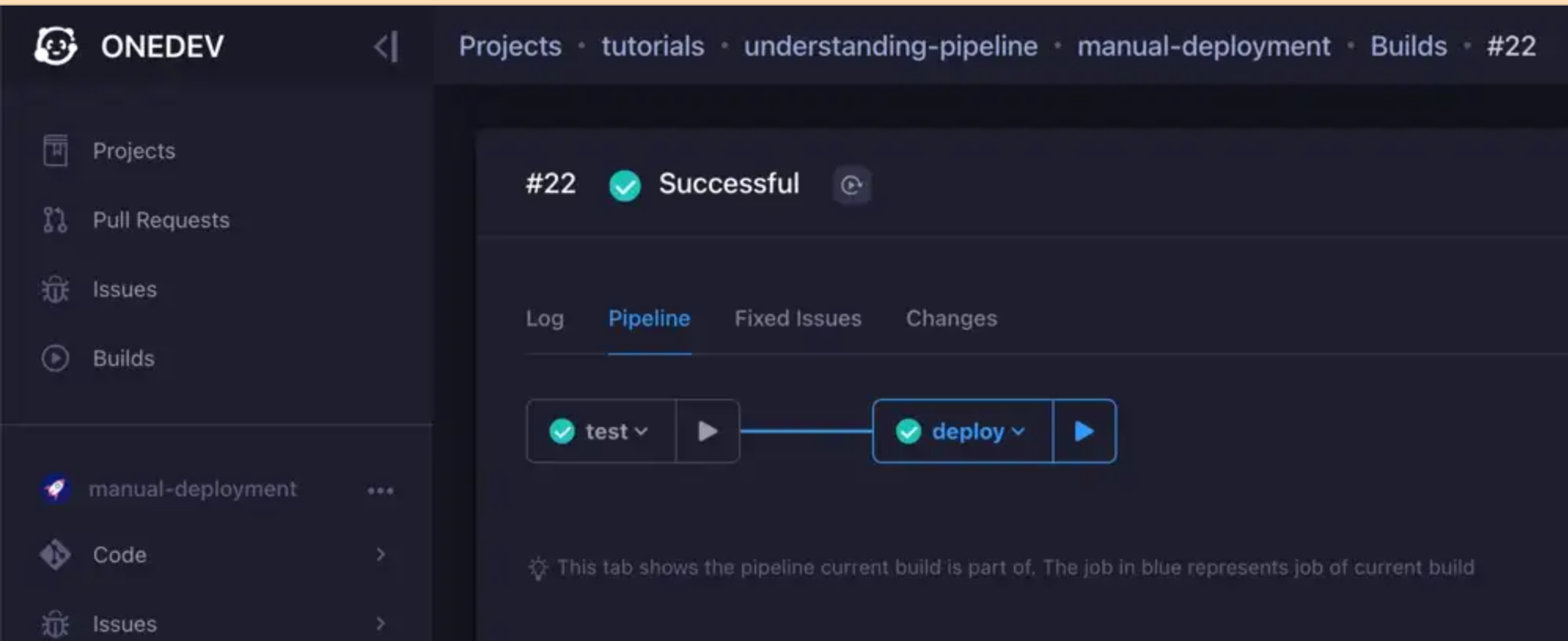 We are currently designing the various builds, but the ones we have defined for the Alexandria client will be a continuous delivery pipeline, like so: 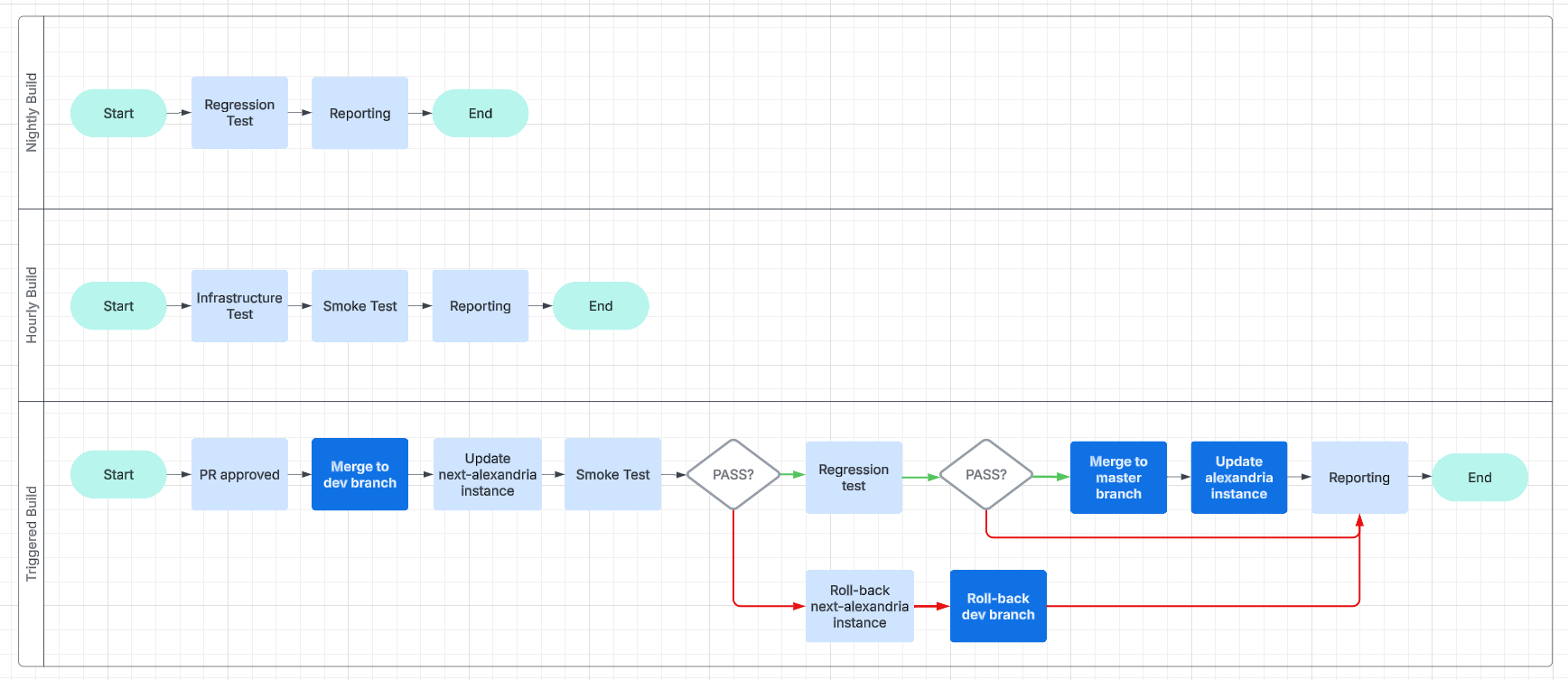 This will make it easier for us to work and collaborate asynchronously and without unnecessary delays. ### Expanding the Status Page  And, finally, we get to the point of all of this busyness: reporting. We are going to have beautiful reports, and we are going to post them online, on our [status page](https://status.gitcitadel.com). We will use bots, to inform Nostriches of the current status of our systems, so go ahead and follow our [GitCitadel DevOps npub](nostr:npub16p0fdr2xccfs07hykx92t0cascac69xjuwaq38kjqy3aawt5hx8s82feyj), to make sure you don't miss out on the IT action. ## Building on stone All in all, we're really happy with the way things are humming along, now, and the steady increase in our productivity, as all the foundational work we've put in starts to pay off. It's getting easier and easier to add new team members, repos, or features/fixes, so we should be able to scale up and out from here. Our GitCitadel is built on a firm foundation. Happy building!
@ fd208ee8:0fd927c1
2025-02-02 10:33:19# GitCitadel Development Operations We, at GitCitadel, have been updating, moving, and rearranging our servers, for quite some time. As a rather large, complex, sprawling project, we have the infrastructure setup to match, so we've decided to give you all a quick run-down of what we are doing behind-the-scenes. ## Supplier Coordination 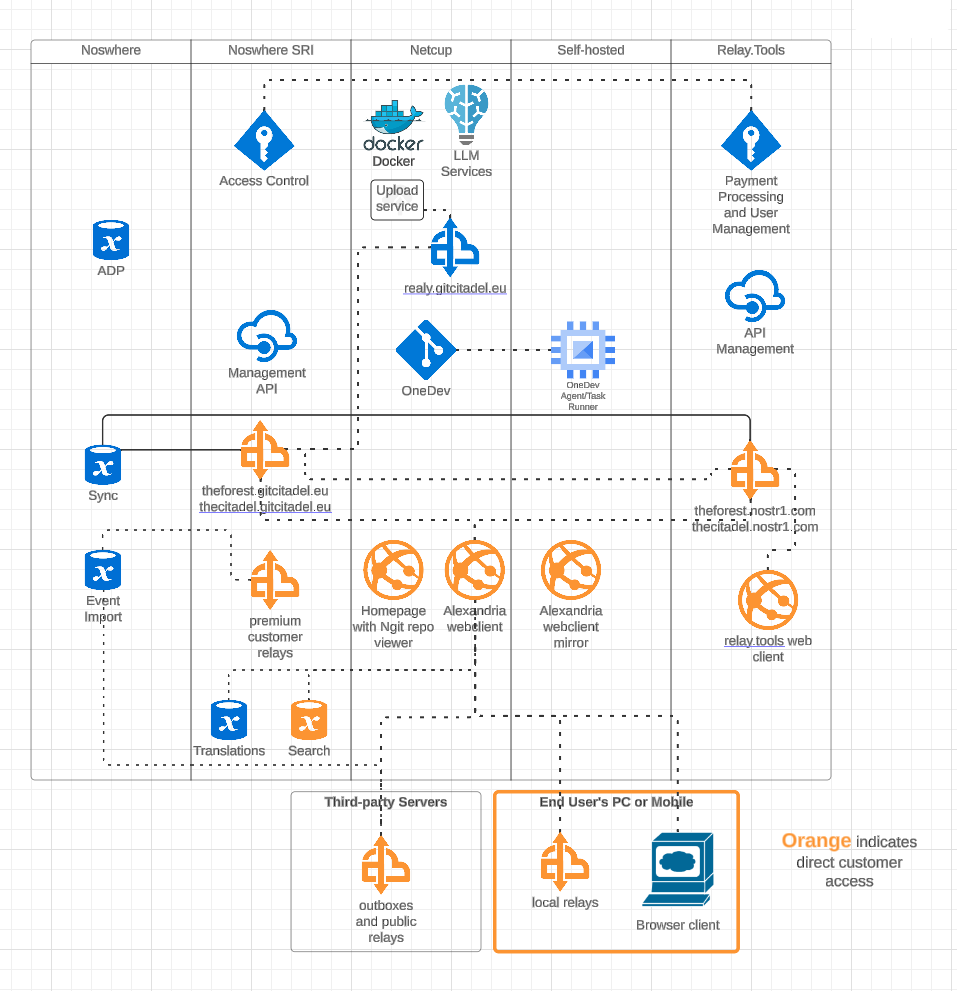 Our first task, this week, was figuring out who would host what where. We have four different locations, where our infra is stored and managed, including two locations from our suppliers. We got that straightened out, quickly, and it's all slowly coming together and being connected and networked. Exciting to watch our DevOps landscape evolve and all of the knowledge-transfer that the interactions provide. ## OneDev Implementation 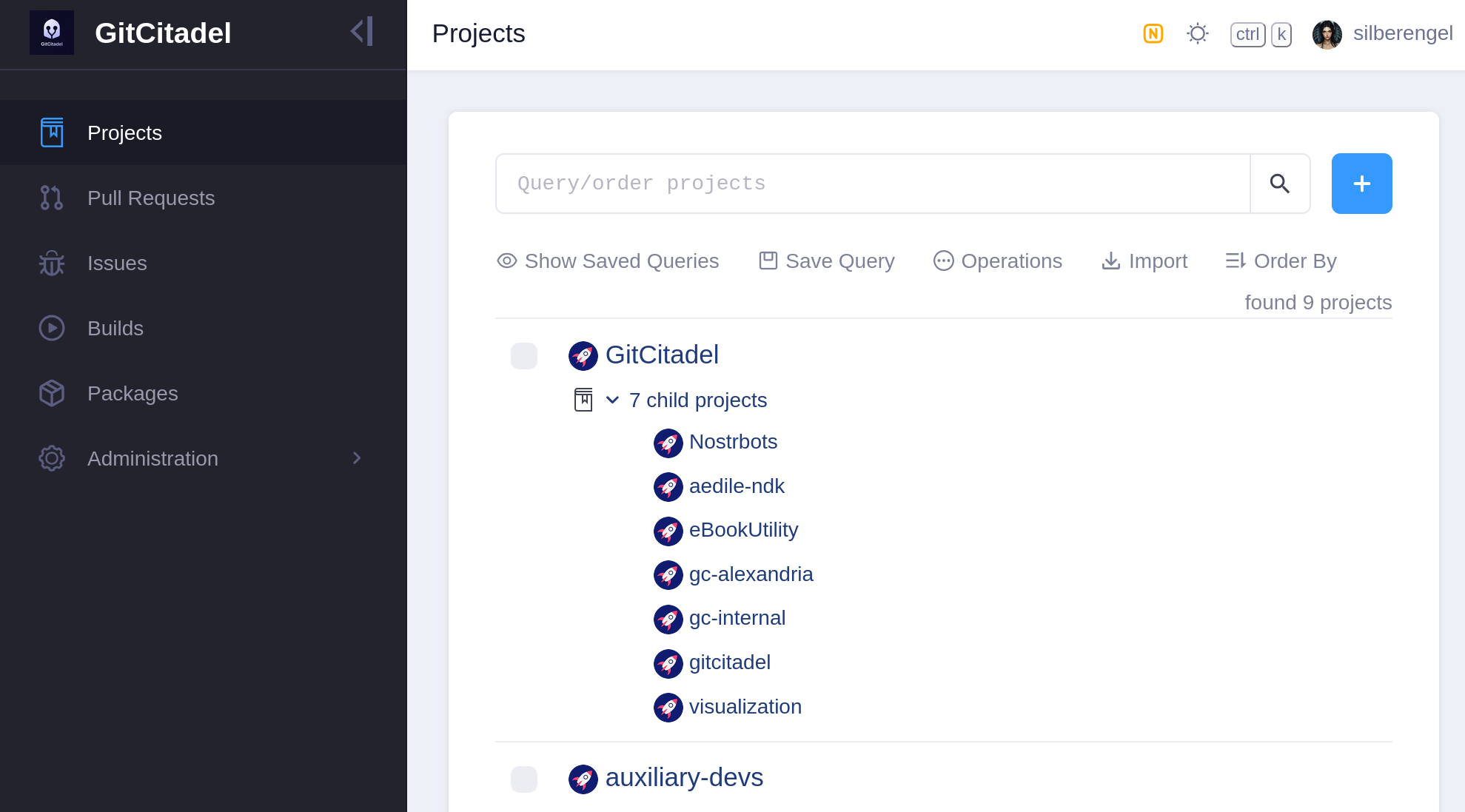 Our biggest internal infra project this week was the migration of all of our issues from Jira, build scripts from Jenkins, and repos from GitHub to a [self-hosted OneDev instance](https://onedev.gitcitadel.eu). In the future, all of our internal build, test, issue, patch/PR, etc. effort will take place there. We also have a separate repo there for communicating with external developers and suppliers. Our [team's GitHub projects](https://github.com/ShadowySupercode) will be demoted to mirrors and a place for external devs to PR to. Public issues and patches will continue to be managed over our self-hosted [GitWorkshop instance](nostr:naddr1qvzqqqrhnypzplfq3m5v3u5r0q9f255fdeyz8nyac6lagssx8zy4wugxjs8ajf7pqy88wumn8ghj7mn0wvhxcmmv9uqq5emfw33kjarpv3jkcs83wav). We're especially glad to finally escape the GitHub Gulag, and avoid being bled dry by Jira fees, without having to give up the important features that we've come to know and love. So, yay! ## Next Infrasteps ### Automated Testing Now, that we have everything tied up in one, neat, backed-up package, we can finally move on to the nitty-gritty and the dirty work. So, we're rolling up our sleeves and writing the Selenium smoke test for our [Alexandria client](https://next-alexandria.gitcitadel.eu). We'll be running that in Docker containers containing different "typical Nostr" images, such as Chrome browser with Nostr Connect signing extension, or Firefox browser with Nos2x-fox extension. Once we get the Nsec Bunker and Amber logins going, we'll add test cases and images for them, as well. (Yes, we can do Bunker. I hope you are in awe at our powers). We are also designing an automated infrastructure test, that will simply rattle through all the various internal and external websites and relays, to make sure that everything is still online and responsive. After that, a Gherkin-based [Behave feature test](https://behave.readthedocs.io/en/latest/) for Alexandria is planned, so that we can prevent regression of completed functionality, from one release to the next. The Gherkin scenarios are written and attached to our stories before development begins (we use acceptance tests as requirements), a manual test-execution is then completed, in order to set the story to *Done*. These completed scenarios will be automated, following each release, with the resulting script linked to from the origin story. 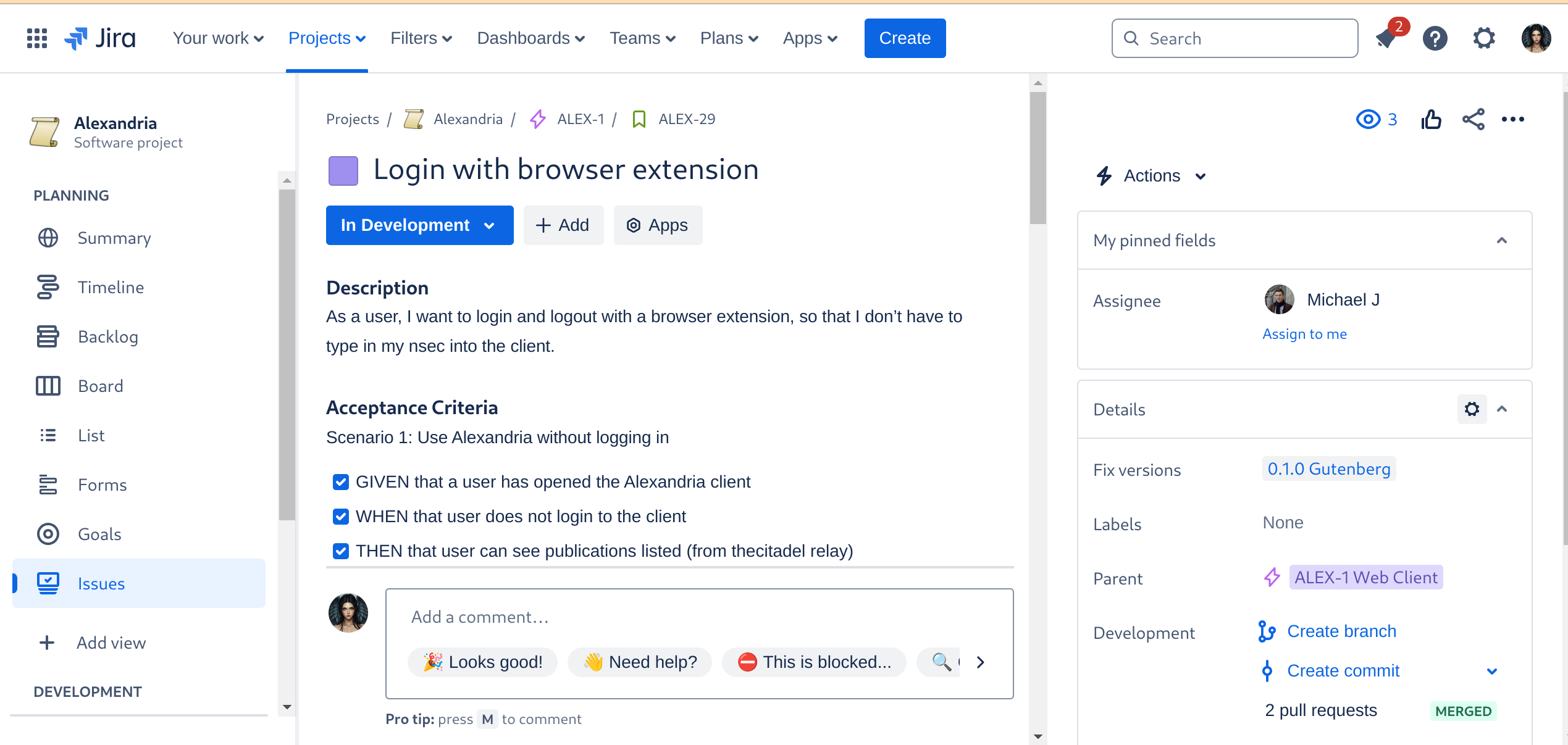 ### Automated Builds As the crowning glory of every DevOps tool chain stands the build automation. This is where everything gets tied together, straightened out, configured, tested, measured, and -- if everything passes the quality gates -- released. I don't have to tell you how much time developers spend staring at the build process display, praying that it all goes through and they can celebrate a Green Wave. 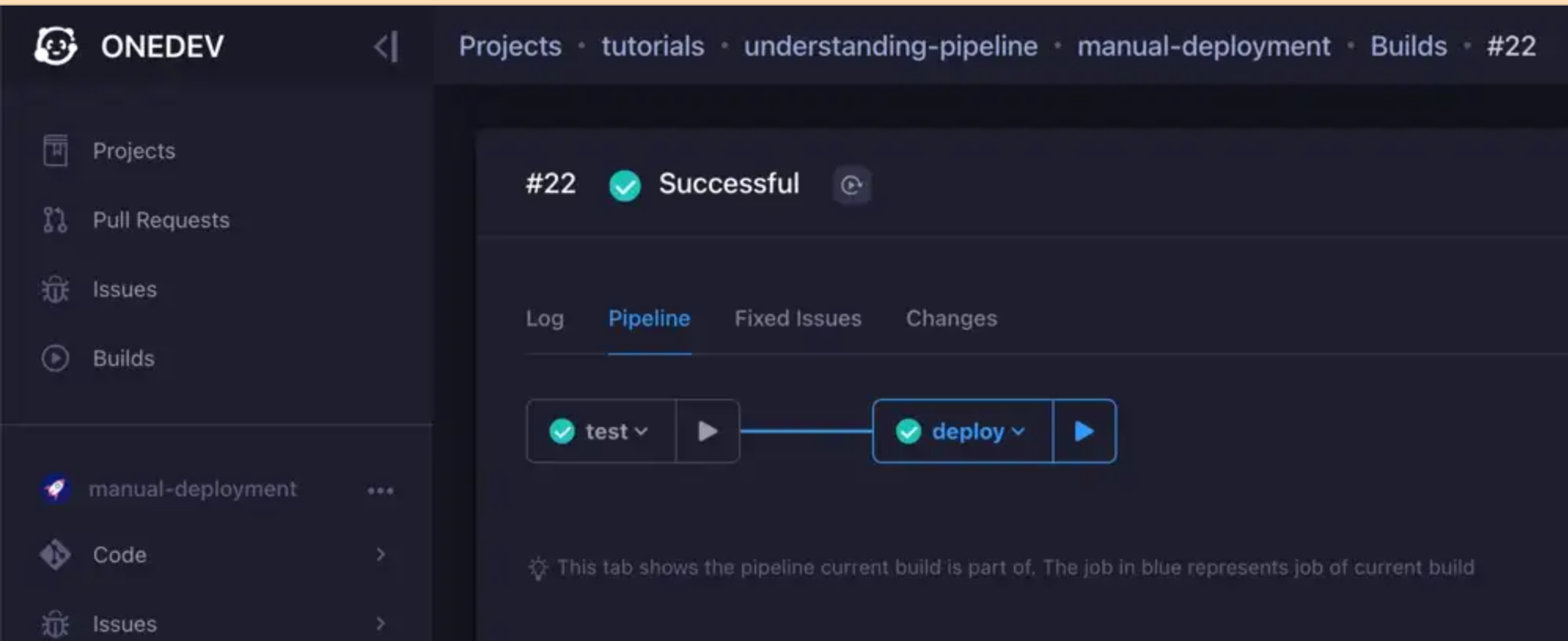 We are currently designing the various builds, but the ones we have defined for the Alexandria client will be a continuous delivery pipeline, like so: 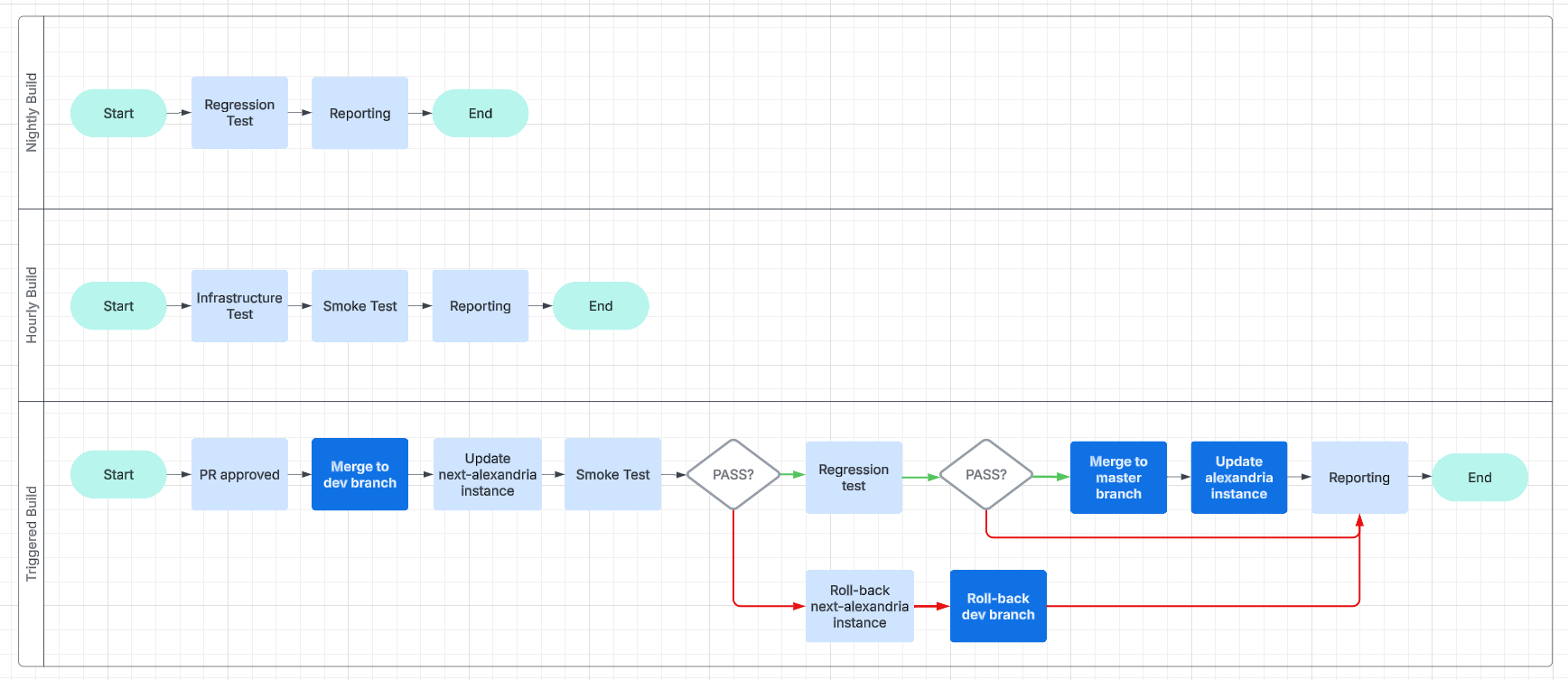 This will make it easier for us to work and collaborate asynchronously and without unnecessary delays. ### Expanding the Status Page  And, finally, we get to the point of all of this busyness: reporting. We are going to have beautiful reports, and we are going to post them online, on our [status page](https://status.gitcitadel.com). We will use bots, to inform Nostriches of the current status of our systems, so go ahead and follow our [GitCitadel DevOps npub](nostr:npub16p0fdr2xccfs07hykx92t0cascac69xjuwaq38kjqy3aawt5hx8s82feyj), to make sure you don't miss out on the IT action. ## Building on stone All in all, we're really happy with the way things are humming along, now, and the steady increase in our productivity, as all the foundational work we've put in starts to pay off. It's getting easier and easier to add new team members, repos, or features/fixes, so we should be able to scale up and out from here. Our GitCitadel is built on a firm foundation. Happy building! @ 9e69e420:d12360c2
2025-02-01 11:16:04 Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.  CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language. One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
@ 9e69e420:d12360c2
2025-02-01 11:16:04 Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.  CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language. One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse. @ d360efec:14907b5f
2025-02-13 05:54:17 **ภาพรวม LUNCUSDT (OKX):** LUNCUSDT กำลังอยู่ในช่วงที่ *มีความผันผวนสูงและมีความไม่แน่นอนมาก* แม้ว่าในอดีต (TF Day) จะเคยมีสัญญาณของการพยายามกลับตัวเป็นขาขึ้น (Breakout EMA 50 และเกิด Golden Cross) แต่ปัจจุบันแรงซื้อเหล่านั้นเริ่มอ่อนแรงลง และมีแรงขายเข้ามาในตลาดมากขึ้น ทำให้เกิดความขัดแย้งระหว่าง Timeframes ต่างๆ  **สถานะปัจจุบัน:** * **แนวโน้ม:** * **TF Day:** เริ่มไม่แน่นอน (จากเดิมที่เป็น Early Uptrend) - แม้ว่าราคาจะยังอยู่เหนือ EMA 50/200 แต่ Money Flow เริ่มแสดงสัญญาณเตือน * **TF4H:** เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50) - Money Flow บ่งบอกถึงแรงขายที่เข้ามา * **TF15:** ผันผวนสูง, ไม่มีทิศทางชัดเจน (Sideways) - Money Flow แสดงถึงแรงขาย แต่ก็มีแรงซื้อกลับเข้ามาบ้าง * **Money Flow (LuxAlgo):** * **TF Day:** แรงซื้อเริ่มอ่อนแรงลงอย่างมีนัยสำคัญ, มีแรงขายเข้ามา * **TF4H:** แรงขายมีมากกว่าแรงซื้อ * **TF15:** แรงขายและแรงซื้อผสมกัน, โดยรวมแรงขายยังมากกว่า * **EMA:** * **TF Day:** EMA 50/200 เป็นแนวรับ/แนวต้าน * **TF4H:** EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวต้าน * **TF15:** EMA 50/200 เป็นแนวต้าน **โครงสร้างราคา (SMC):** | Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) | | :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- | | Day | ด้านบนและล่าง | ด้านบน | เริ่มก่อตัว (แต่ไม่แข็งแกร่ง) | - | | 4H | ด้านบน | ด้านบน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | มี EQH หลายจุด | | 15m | ด้านบนและล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | มี EQH และ EQL หลายจุด | **แนวรับ-แนวต้านสำคัญ:** | Timeframe | แนวรับ | แนวต้าน | | :-------- | :----------------------------------------------------------- | :--------------------------------------------------------------------- | | Day | EMA 50 (≈0.00010000), EMA 200 (≈0.00008000), 0.00006000-0.00007000 | 0.00017953 (High ล่าสุด), 0.00014000 (Volume Profile) | | 4H | EMA 50 (≈0.00007000), 0.00006000-0.00007000 | EMA 200 (≈0.00008000), 0.00008132, บริเวณ 0.00010000-0.00012000 (EQH) | | 15m | บริเวณ Low ล่าสุด | EMA 50, EMA 200, บริเวณ 0.000075-0.000076 (EQH) | **กลยุทธ์ (LUNCUSDT):** 1. **Wait & See (ทางเลือกที่ดีที่สุด):** * **เหตุผล:** ความขัดแย้งระหว่าง Timeframes สูงมาก, แนวโน้มไม่ชัดเจน, Money Flow ใน TF4H และ TF15 เป็นลบ * รอให้ราคาแสดงทิศทางที่ชัดเจนกว่านี้ (ยืนเหนือ EMA 50 ใน TF4H ได้, Breakout แนวต้านใน TF15) 2. **Buy on Dip (Day, 4H) - *ความเสี่ยงสูงมาก ไม่แนะนำ*:** * **เหตุผล:** แนวโน้มระยะยาวอาจจะยังเป็นขาขึ้นได้ (ถ้าไม่หลุดแนวรับสำคัญ) * **เงื่อนไข:** *ต้อง* รอสัญญาณการกลับตัวใน TF15 ก่อน * **จุดเข้า:** พิจารณาเฉพาะบริเวณแนวรับที่แข็งแกร่งมากๆ (EMA ของ Day/4H) *และต้องดู TF15 ประกอบ* * **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 3. **Short (15, ความเสี่ยงสูงมาก):** * **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ * **เงื่อนไข:** ราคาไม่สามารถ Breakout EMA หรือแนวต้านอื่นๆ ใน TF15 ได้ * **จุดเข้า:** บริเวณ EMA หรือแนวต้านของ TF15 * **Stop Loss:** เหนือ High ล่าสุดของ TF15 **คำแนะนำ (เน้นย้ำ):** * **LUNC เป็นเหรียญที่มีความเสี่ยงสูงมาก (High Risk):** มีความผันผวนสูง และอาจมีการเปลี่ยนแปลงอย่างรวดเร็ว * **ความขัดแย้งของ Timeframes:** สถานการณ์ของ LUNCUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง * **Money Flow:** บ่งบอกถึงแรงขายที่เริ่มเข้ามา และแนวโน้มขาขึ้น (ระยะกลาง-ยาว) ที่อ่อนแอลง * **ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด:** "รอ" เป็นกลยุทธ์ที่ดีที่สุด * **Risk Management:** สำคัญที่สุด ไม่ว่าจะเลือกกลยุทธ์ใด ต้องมีการบริหารความเสี่ยงที่ดี **สรุป:** LUNCUSDT กำลังอยู่ในช่วงเวลาที่ยากลำบากและมีความเสี่ยงสูงมากที่สุดในบรรดา 3 เหรียญที่เราวิเคราะห์กันมา การตัดสินใจที่ผิดพลาดอาจนำไปสู่การขาดทุนได้ ควรพิจารณาอย่างรอบคอบก่อนเข้าเทรดทุกครั้ง และ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดสำหรับนักลงทุนส่วนใหญ่ค่ะ **Disclaimer:** การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
@ d360efec:14907b5f
2025-02-13 05:54:17 **ภาพรวม LUNCUSDT (OKX):** LUNCUSDT กำลังอยู่ในช่วงที่ *มีความผันผวนสูงและมีความไม่แน่นอนมาก* แม้ว่าในอดีต (TF Day) จะเคยมีสัญญาณของการพยายามกลับตัวเป็นขาขึ้น (Breakout EMA 50 และเกิด Golden Cross) แต่ปัจจุบันแรงซื้อเหล่านั้นเริ่มอ่อนแรงลง และมีแรงขายเข้ามาในตลาดมากขึ้น ทำให้เกิดความขัดแย้งระหว่าง Timeframes ต่างๆ  **สถานะปัจจุบัน:** * **แนวโน้ม:** * **TF Day:** เริ่มไม่แน่นอน (จากเดิมที่เป็น Early Uptrend) - แม้ว่าราคาจะยังอยู่เหนือ EMA 50/200 แต่ Money Flow เริ่มแสดงสัญญาณเตือน * **TF4H:** เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50) - Money Flow บ่งบอกถึงแรงขายที่เข้ามา * **TF15:** ผันผวนสูง, ไม่มีทิศทางชัดเจน (Sideways) - Money Flow แสดงถึงแรงขาย แต่ก็มีแรงซื้อกลับเข้ามาบ้าง * **Money Flow (LuxAlgo):** * **TF Day:** แรงซื้อเริ่มอ่อนแรงลงอย่างมีนัยสำคัญ, มีแรงขายเข้ามา * **TF4H:** แรงขายมีมากกว่าแรงซื้อ * **TF15:** แรงขายและแรงซื้อผสมกัน, โดยรวมแรงขายยังมากกว่า * **EMA:** * **TF Day:** EMA 50/200 เป็นแนวรับ/แนวต้าน * **TF4H:** EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวต้าน * **TF15:** EMA 50/200 เป็นแนวต้าน **โครงสร้างราคา (SMC):** | Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) | | :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- | | Day | ด้านบนและล่าง | ด้านบน | เริ่มก่อตัว (แต่ไม่แข็งแกร่ง) | - | | 4H | ด้านบน | ด้านบน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | มี EQH หลายจุด | | 15m | ด้านบนและล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | มี EQH และ EQL หลายจุด | **แนวรับ-แนวต้านสำคัญ:** | Timeframe | แนวรับ | แนวต้าน | | :-------- | :----------------------------------------------------------- | :--------------------------------------------------------------------- | | Day | EMA 50 (≈0.00010000), EMA 200 (≈0.00008000), 0.00006000-0.00007000 | 0.00017953 (High ล่าสุด), 0.00014000 (Volume Profile) | | 4H | EMA 50 (≈0.00007000), 0.00006000-0.00007000 | EMA 200 (≈0.00008000), 0.00008132, บริเวณ 0.00010000-0.00012000 (EQH) | | 15m | บริเวณ Low ล่าสุด | EMA 50, EMA 200, บริเวณ 0.000075-0.000076 (EQH) | **กลยุทธ์ (LUNCUSDT):** 1. **Wait & See (ทางเลือกที่ดีที่สุด):** * **เหตุผล:** ความขัดแย้งระหว่าง Timeframes สูงมาก, แนวโน้มไม่ชัดเจน, Money Flow ใน TF4H และ TF15 เป็นลบ * รอให้ราคาแสดงทิศทางที่ชัดเจนกว่านี้ (ยืนเหนือ EMA 50 ใน TF4H ได้, Breakout แนวต้านใน TF15) 2. **Buy on Dip (Day, 4H) - *ความเสี่ยงสูงมาก ไม่แนะนำ*:** * **เหตุผล:** แนวโน้มระยะยาวอาจจะยังเป็นขาขึ้นได้ (ถ้าไม่หลุดแนวรับสำคัญ) * **เงื่อนไข:** *ต้อง* รอสัญญาณการกลับตัวใน TF15 ก่อน * **จุดเข้า:** พิจารณาเฉพาะบริเวณแนวรับที่แข็งแกร่งมากๆ (EMA ของ Day/4H) *และต้องดู TF15 ประกอบ* * **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 3. **Short (15, ความเสี่ยงสูงมาก):** * **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ * **เงื่อนไข:** ราคาไม่สามารถ Breakout EMA หรือแนวต้านอื่นๆ ใน TF15 ได้ * **จุดเข้า:** บริเวณ EMA หรือแนวต้านของ TF15 * **Stop Loss:** เหนือ High ล่าสุดของ TF15 **คำแนะนำ (เน้นย้ำ):** * **LUNC เป็นเหรียญที่มีความเสี่ยงสูงมาก (High Risk):** มีความผันผวนสูง และอาจมีการเปลี่ยนแปลงอย่างรวดเร็ว * **ความขัดแย้งของ Timeframes:** สถานการณ์ของ LUNCUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง * **Money Flow:** บ่งบอกถึงแรงขายที่เริ่มเข้ามา และแนวโน้มขาขึ้น (ระยะกลาง-ยาว) ที่อ่อนแอลง * **ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด:** "รอ" เป็นกลยุทธ์ที่ดีที่สุด * **Risk Management:** สำคัญที่สุด ไม่ว่าจะเลือกกลยุทธ์ใด ต้องมีการบริหารความเสี่ยงที่ดี **สรุป:** LUNCUSDT กำลังอยู่ในช่วงเวลาที่ยากลำบากและมีความเสี่ยงสูงมากที่สุดในบรรดา 3 เหรียญที่เราวิเคราะห์กันมา การตัดสินใจที่ผิดพลาดอาจนำไปสู่การขาดทุนได้ ควรพิจารณาอย่างรอบคอบก่อนเข้าเทรดทุกครั้ง และ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดสำหรับนักลงทุนส่วนใหญ่ค่ะ **Disclaimer:** การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ @ d360efec:14907b5f
2025-02-13 05:27:39 **ภาพรวม XRPUSDT (OKX):** XRPUSDT กำลังอยู่ในช่วงสำคัญ แนวโน้มระยะยาว (TF Day) เริ่มมีสัญญาณบวกของการเป็นขาขึ้น (Early Uptrend) หลังราคา Breakout EMA 50 และ Money Flow สนับสนุน อย่างไรก็ตาม แนวโน้มระยะกลาง (TF4H) เริ่มแสดงความอ่อนแอลง โดยราคาพักตัวลงมาทดสอบแนวรับสำคัญ และ Money Flow บ่งชี้ถึงแรงซื้อที่ลดลงและแรงขายที่เพิ่มขึ้น ส่วนแนวโน้มระยะสั้นมาก (TF15) เป็นขาลงชัดเจน  **แนวโน้ม:** * **TF Day:** เริ่มเป็นขาขึ้น (Early Uptrend) - Breakout EMA 50, Money Flow เป็นบวก * **TF4H:** เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50 และ EQL) - Money Flow เริ่มเป็นลบ * **TF15:** ขาลง (Downtrend) ระยะสั้นมาก - ราคาหลุด EMA, โครงสร้างราคาเป็น Lower Highs/Lows, Money Flow เป็นลบ **โครงสร้างราคา (SMC):** | Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) | | :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- | | Day | ด้านบน (Breakout EMA 50) | ไม่ชัดเจน | เริ่มก่อตัว (แต่ยังไม่ชัดเจน) | - | | 4H | ด้านบน | ไม่ชัดเจน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | EQH: 3.00-3.20, EQL: 2.2667 | | 15m | ด้านล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | EQH: 2.48-2.50, EQL: 2.38 |  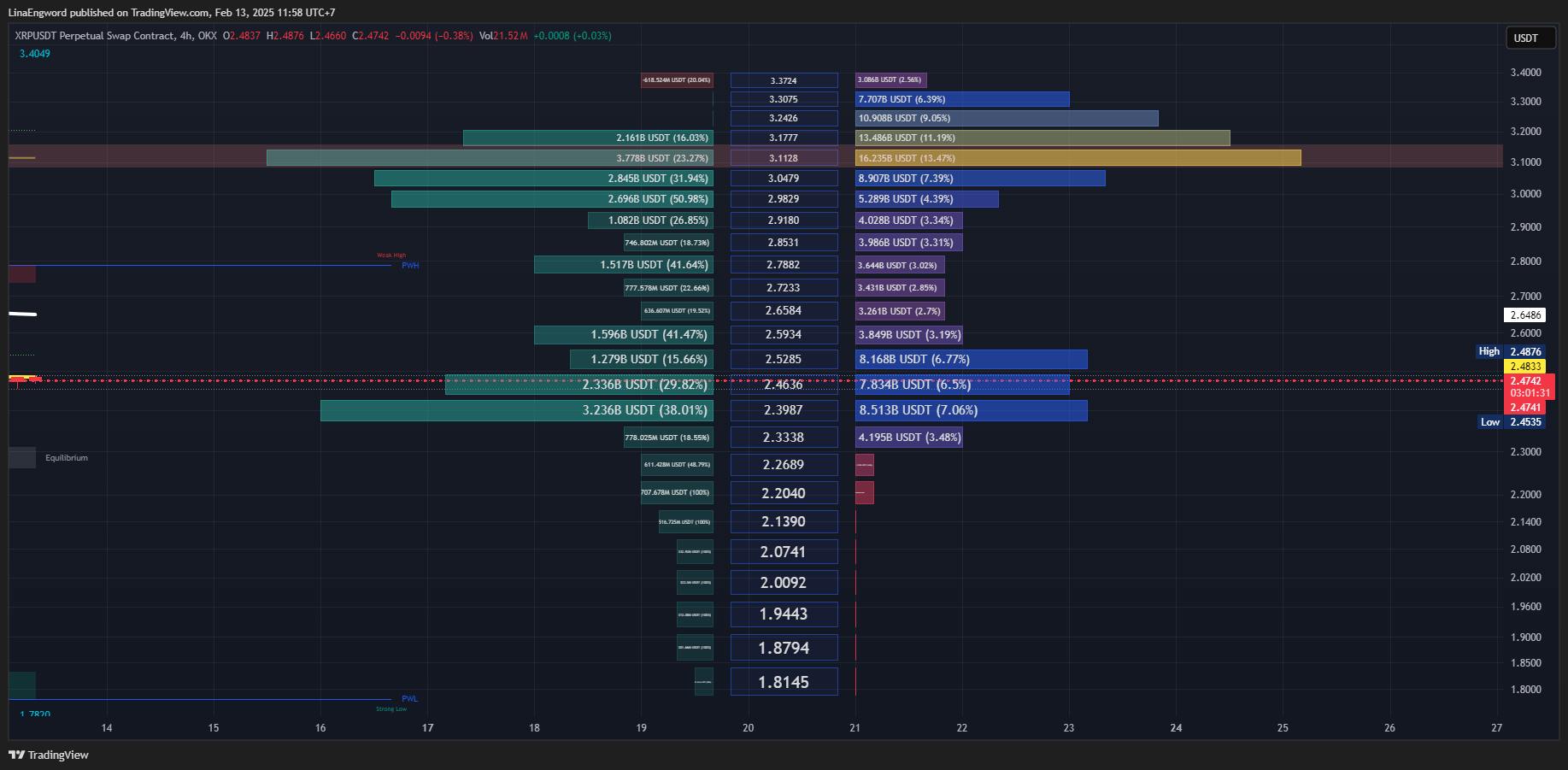 **Money Flow (LuxAlgo):** * **TF Day:** แรงซื้อแข็งแกร่ง * **TF4H:** แรงซื้อเริ่มอ่อนแรงลง, แรงขายเริ่มเข้ามา * **TF15:** แรงขายมีอิทธิพลเหนือกว่า **EMA (Exponential Moving Average):** * **TF Day:** EMA 50 & 200 เป็นแนวรับ * **TF4H:** EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวรับถัดไป * **TF15:** EMA 50 & 200 เป็นแนวต้าน **แนวรับ-แนวต้านสำคัญ:** | Timeframe | แนวรับ | แนวต้าน | | :-------- | :----------------------------------------------------- | :----------------------------------------------------------------------- | | Day | EMA 50 (≈1.56), EMA 200 (≈1.08) | 3.4049 (High), 3.00-3.20 (EQH) | | 4H | EMA 50 (≈2.20), *2.2667 (EQL)*, EMA 200, 1.7820 | 3.4049, 2.3987 (Volume Profile), 3.00-3.20 (EQH) | | 15m | 2.38 (EQL, Volume Profile), 2.3274 | EMA 50, EMA 200, 2.4196, Equilibrium (≈2.44), 2.48-2.50 (EQH) | **กลยุทธ์ (XRPUSDT):** 1. **Wait & See (ทางเลือกที่ดีที่สุด):** * **เหตุผล:** ความขัดแย้งระหว่าง Timeframes สูง, TF4H กำลังทดสอบแนวรับสำคัญ, Money Flow ใน TF4H และ TF15 เป็นลบ * รอให้ราคาแสดงทิศทางที่ชัดเจน (ยืนเหนือ EMA 50 ใน TF4H ได้ หรือ Breakout แนวต้านใน TF15) 2. **Buy on Dip (Day, 4H) - *ความเสี่ยงสูงมาก*:** * **เหตุผล:** แนวโน้มระยะยาวยังมีโอกาสเป็นขาขึ้น, Money Flow ใน TF Day เป็นบวก * **เงื่อนไข (สำคัญมาก):** *ต้อง* รอสัญญาณการกลับตัวใน TF15 ก่อน เช่น: * Breakout แนวต้านย่อยๆ พร้อม Volume * Money Flow (TF15) เปลี่ยนเป็นสีเขียว * Bullish Candlestick Patterns * **จุดเข้า (Day):** EMA 50, EMA 200 (*ดู TF15 ประกอบ*) * **จุดเข้า (4H):** EMA 50, *2.2667 (EQL)* (*ดู TF15 ประกอบ*) * **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ 3. **Short (15, ความเสี่ยงสูงมาก):** * **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ * **เงื่อนไข:** ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้ * **จุดเข้า:** บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ * **Stop Loss:** เหนือ High ล่าสุดของ TF15 **คำแนะนำ:** * **ความขัดแย้งของ Timeframes:** XRPUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง * **Money Flow:** Day เป็นบวก, 4H เริ่มเป็นลบ, 15m เป็นลบ * **EMA 50 (TF4H) & EQL 2.2667:** จุดชี้ชะตา * **ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด:** "รอ" ดีที่สุด * **Risk Management:** สำคัญที่สุด **สรุป:** สถานการณ์ของ XRPUSDT ตอนนี้มีความเสี่ยงสูงมาก และไม่เหมาะกับนักลงทุนที่รับความเสี่ยงได้ต่ำ การ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดค่ะ Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
@ d360efec:14907b5f
2025-02-13 05:27:39 **ภาพรวม XRPUSDT (OKX):** XRPUSDT กำลังอยู่ในช่วงสำคัญ แนวโน้มระยะยาว (TF Day) เริ่มมีสัญญาณบวกของการเป็นขาขึ้น (Early Uptrend) หลังราคา Breakout EMA 50 และ Money Flow สนับสนุน อย่างไรก็ตาม แนวโน้มระยะกลาง (TF4H) เริ่มแสดงความอ่อนแอลง โดยราคาพักตัวลงมาทดสอบแนวรับสำคัญ และ Money Flow บ่งชี้ถึงแรงซื้อที่ลดลงและแรงขายที่เพิ่มขึ้น ส่วนแนวโน้มระยะสั้นมาก (TF15) เป็นขาลงชัดเจน  **แนวโน้ม:** * **TF Day:** เริ่มเป็นขาขึ้น (Early Uptrend) - Breakout EMA 50, Money Flow เป็นบวก * **TF4H:** เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50 และ EQL) - Money Flow เริ่มเป็นลบ * **TF15:** ขาลง (Downtrend) ระยะสั้นมาก - ราคาหลุด EMA, โครงสร้างราคาเป็น Lower Highs/Lows, Money Flow เป็นลบ **โครงสร้างราคา (SMC):** | Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) | | :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- | | Day | ด้านบน (Breakout EMA 50) | ไม่ชัดเจน | เริ่มก่อตัว (แต่ยังไม่ชัดเจน) | - | | 4H | ด้านบน | ไม่ชัดเจน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | EQH: 3.00-3.20, EQL: 2.2667 | | 15m | ด้านล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | EQH: 2.48-2.50, EQL: 2.38 |  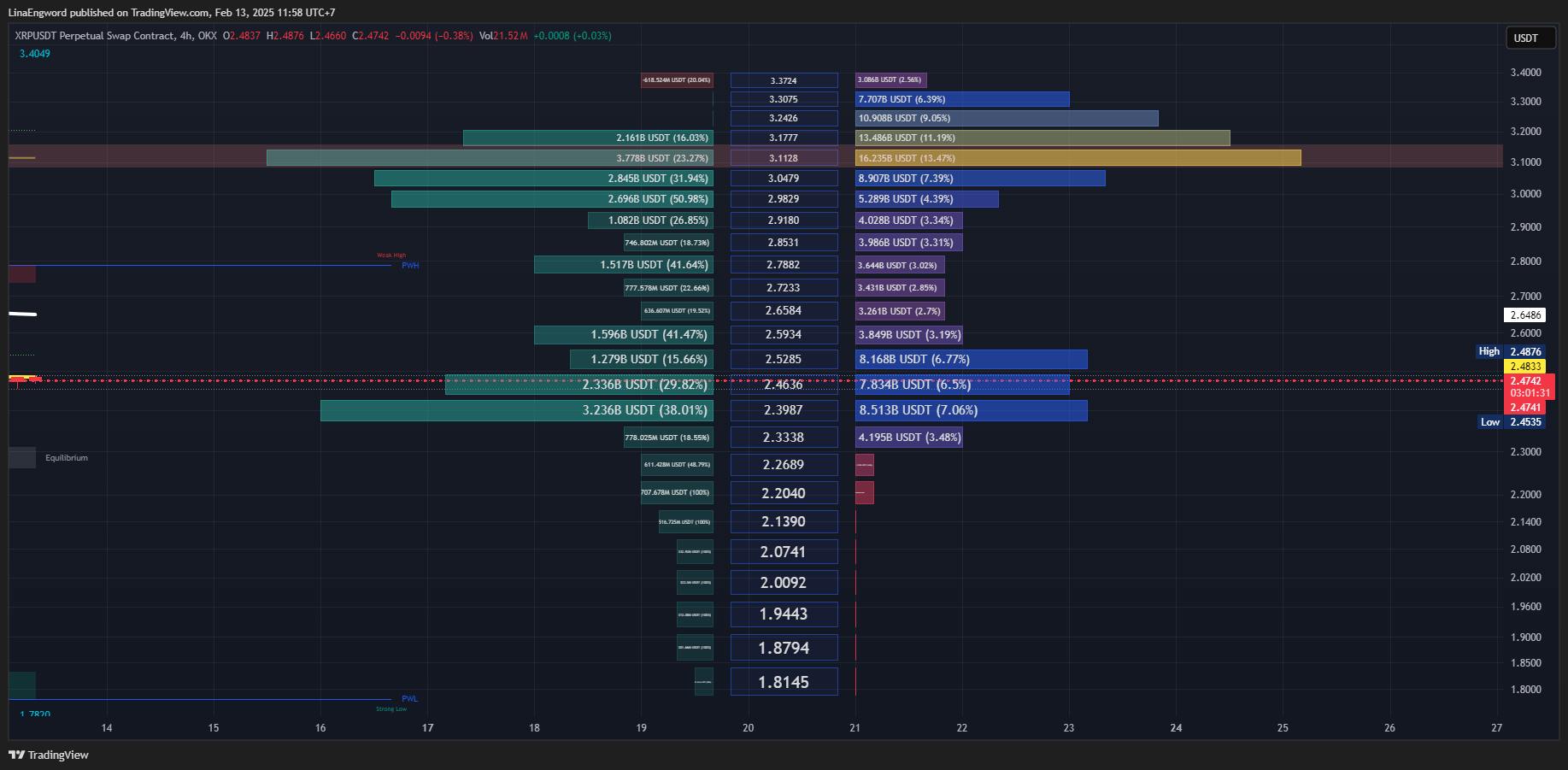 **Money Flow (LuxAlgo):** * **TF Day:** แรงซื้อแข็งแกร่ง * **TF4H:** แรงซื้อเริ่มอ่อนแรงลง, แรงขายเริ่มเข้ามา * **TF15:** แรงขายมีอิทธิพลเหนือกว่า **EMA (Exponential Moving Average):** * **TF Day:** EMA 50 & 200 เป็นแนวรับ * **TF4H:** EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวรับถัดไป * **TF15:** EMA 50 & 200 เป็นแนวต้าน **แนวรับ-แนวต้านสำคัญ:** | Timeframe | แนวรับ | แนวต้าน | | :-------- | :----------------------------------------------------- | :----------------------------------------------------------------------- | | Day | EMA 50 (≈1.56), EMA 200 (≈1.08) | 3.4049 (High), 3.00-3.20 (EQH) | | 4H | EMA 50 (≈2.20), *2.2667 (EQL)*, EMA 200, 1.7820 | 3.4049, 2.3987 (Volume Profile), 3.00-3.20 (EQH) | | 15m | 2.38 (EQL, Volume Profile), 2.3274 | EMA 50, EMA 200, 2.4196, Equilibrium (≈2.44), 2.48-2.50 (EQH) | **กลยุทธ์ (XRPUSDT):** 1. **Wait & See (ทางเลือกที่ดีที่สุด):** * **เหตุผล:** ความขัดแย้งระหว่าง Timeframes สูง, TF4H กำลังทดสอบแนวรับสำคัญ, Money Flow ใน TF4H และ TF15 เป็นลบ * รอให้ราคาแสดงทิศทางที่ชัดเจน (ยืนเหนือ EMA 50 ใน TF4H ได้ หรือ Breakout แนวต้านใน TF15) 2. **Buy on Dip (Day, 4H) - *ความเสี่ยงสูงมาก*:** * **เหตุผล:** แนวโน้มระยะยาวยังมีโอกาสเป็นขาขึ้น, Money Flow ใน TF Day เป็นบวก * **เงื่อนไข (สำคัญมาก):** *ต้อง* รอสัญญาณการกลับตัวใน TF15 ก่อน เช่น: * Breakout แนวต้านย่อยๆ พร้อม Volume * Money Flow (TF15) เปลี่ยนเป็นสีเขียว * Bullish Candlestick Patterns * **จุดเข้า (Day):** EMA 50, EMA 200 (*ดู TF15 ประกอบ*) * **จุดเข้า (4H):** EMA 50, *2.2667 (EQL)* (*ดู TF15 ประกอบ*) * **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ 3. **Short (15, ความเสี่ยงสูงมาก):** * **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ * **เงื่อนไข:** ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้ * **จุดเข้า:** บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ * **Stop Loss:** เหนือ High ล่าสุดของ TF15 **คำแนะนำ:** * **ความขัดแย้งของ Timeframes:** XRPUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง * **Money Flow:** Day เป็นบวก, 4H เริ่มเป็นลบ, 15m เป็นลบ * **EMA 50 (TF4H) & EQL 2.2667:** จุดชี้ชะตา * **ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด:** "รอ" ดีที่สุด * **Risk Management:** สำคัญที่สุด **สรุป:** สถานการณ์ของ XRPUSDT ตอนนี้มีความเสี่ยงสูงมาก และไม่เหมาะกับนักลงทุนที่รับความเสี่ยงได้ต่ำ การ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดค่ะ Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ @ bf6e4fe1:46d21f26
2025-01-31 01:51:03{"title":"test","content":"test"}
@ bf6e4fe1:46d21f26
2025-01-31 01:51:03{"title":"test","content":"test"} @ d360efec:14907b5f
2025-02-13 04:47:20 **ภาพรวม BTCUSDT :** Bitcoin (BTCUSDT) กำลังอยู่ในช่วงสำคัญ แม้ว่าแนวโน้มหลักในระยะกลางถึงยาว (TF Day & 4H) จะยังคงเป็นขาขึ้นที่แข็งแกร่ง แต่ในระยะสั้นมาก (TF15) กลับแสดงสัญญาณของความอ่อนแอและการปรับฐานลงมา ทำให้เกิดความไม่แน่นอนในทิศทางของราคา อย่างไรก็ตาม *Money Flow ใน TF Day บ่งชี้ว่าแรงซื้อโดยรวมยังคงแข็งแกร่ง*  **แนวโน้ม:** * **TF Day:** ขาขึ้น (Uptrend) แข็งแกร่ง – ราคาอยู่เหนือ EMA 50 และ EMA 200, โครงสร้างราคาเป็น Higher Highs (HH) และ Higher Lows (HL), *Money Flow เป็นบวก (แรงซื้อ)* * **TF4H:** ขาขึ้น (Uptrend) – ราคาอยู่เหนือ EMA, มีการพักตัวลงมา (Pullback) แต่ยังไม่เสียโครงสร้างขาขึ้น, *Money Flow เริ่มอ่อนแรง (แรงซื้อลดลง, แรงขายเพิ่มขึ้น)* * **TF15:** ขาลง (Downtrend) ระยะสั้นมาก – ราคาหลุด EMA และแนวรับย่อย, โครงสร้างราคาเป็น Lower Highs (LH) และ Lower Lows (LL), *Money Flow เป็นลบ (แรงขาย)* **โครงสร้างราคา (SMC):** * **TF Day:** ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS) * **TF4H:** ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS), มี Equal Highs (EQH) ที่เป็นแนวต้าน * **TF15:** บ่งบอกถึงแนวโน้มขาลงระยะสั้น (BOS ด้านล่าง, LH, LL), มี EQH เป็นแนวต้าน **Money Flow (LuxAlgo) - สรุป:** * **TF Day:** แรงซื้อยังคงแข็งแกร่งอย่างชัดเจน * **TF4H:** แรงซื้อเริ่มอ่อนแรงลง, มีแรงขายเข้ามา * **TF15:** แรงขายมีอิทธิพลเหนือกว่า  **EMA (Exponential Moving Average):** * **TF Day & 4H:** EMA 50 & 200 เป็นแนวรับสำคัญ * **TF15:** EMA 50 & 200 กลายเป็นแนวต้าน **แนวรับ-แนวต้านสำคัญ:** | Timeframe | แนวรับ | แนวต้าน | | :-------- | :------------------------------------------------------------------------- | :-------------------------------------------------------------- | | Day | EMA 50, EMA 200, 96,000-98,000, 85,724.7 | 109,998.9 (High เดิม) | | 4H | EMA 50, EMA 200, 96,000-98,000, 89,037.0 | 109,998.9 (EQH, High เดิม) | | 15m | 95,200 (Low ล่าสุด), 94,707.4 (Low ก่อนหน้า) | EMA 50, EMA 200, บริเวณ 96,000, 96,807.8, 97,000-97,200 | **กลยุทธ์ (BTCUSDT):** 1. **Buy on Dip (Day, 4H) - *มีความน่าเชื่อถือมากขึ้น แต่ยังคงต้องระมัดระวัง*:** * **เหตุผล:** แนวโน้มหลักยังเป็นขาขึ้น, Money Flow ใน TF Day แข็งแกร่ง * **เงื่อนไข:** *ยังคงต้องรอสัญญาณการกลับตัวของราคาใน TF15 ก่อน* (Breakout แนวต้านย่อย, Money Flow TF15 เป็นบวก, Bullish Candlestick Patterns) * **จุดเข้า (Day):** EMA 50, EMA 200, บริเวณ 96,000-98,000 * **จุดเข้า (4H):** EMA 50 * **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ 2. **Short (15, ความเสี่ยงสูงมาก):** * **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow TF15 เป็นลบ * **เงื่อนไข:** ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้ * **จุดเข้า:** บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ * **Stop Loss:** เหนือ High ล่าสุดของ TF15 3. **Wait & See (ทางเลือกที่ปลอดภัย):** * **เหตุผล:** ความขัดแย้งระหว่าง Timeframes ยังคงมีอยู่ * รอให้ตลาดเฉลยทิศทางที่ชัดเจนกว่านี้ **คำแนะนำ (เน้นย้ำ):** * **Money Flow ใน TF Day:** เป็นปัจจัยบวกที่สำคัญ ทำให้กลยุทธ์ Buy on Dip มีน้ำหนักมากขึ้น * **ความขัดแย้งของ Timeframes:** ยังคงต้องระวัง TF15 ที่เป็นขาลง * **Volume:** การ Breakout/Breakdown ใดๆ ควรมี Volume สนับสนุน * **Risk Management:** สำคัญที่สุด **สรุป:** สถานการณ์ของ BTCUSDT โดยรวมยังคงเป็นบวก (ขาขึ้น) แต่มีความเสี่ยงในระยะสั้นจาก TF15 การตัดสินใจลงทุนควรพิจารณาจาก Timeframe ที่เหมาะสมกับสไตล์การเทรดของคุณ และอย่าลืมบริหารความเสี่ยงเสมอค่ะ **Disclaimer:** การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
@ d360efec:14907b5f
2025-02-13 04:47:20 **ภาพรวม BTCUSDT :** Bitcoin (BTCUSDT) กำลังอยู่ในช่วงสำคัญ แม้ว่าแนวโน้มหลักในระยะกลางถึงยาว (TF Day & 4H) จะยังคงเป็นขาขึ้นที่แข็งแกร่ง แต่ในระยะสั้นมาก (TF15) กลับแสดงสัญญาณของความอ่อนแอและการปรับฐานลงมา ทำให้เกิดความไม่แน่นอนในทิศทางของราคา อย่างไรก็ตาม *Money Flow ใน TF Day บ่งชี้ว่าแรงซื้อโดยรวมยังคงแข็งแกร่ง*  **แนวโน้ม:** * **TF Day:** ขาขึ้น (Uptrend) แข็งแกร่ง – ราคาอยู่เหนือ EMA 50 และ EMA 200, โครงสร้างราคาเป็น Higher Highs (HH) และ Higher Lows (HL), *Money Flow เป็นบวก (แรงซื้อ)* * **TF4H:** ขาขึ้น (Uptrend) – ราคาอยู่เหนือ EMA, มีการพักตัวลงมา (Pullback) แต่ยังไม่เสียโครงสร้างขาขึ้น, *Money Flow เริ่มอ่อนแรง (แรงซื้อลดลง, แรงขายเพิ่มขึ้น)* * **TF15:** ขาลง (Downtrend) ระยะสั้นมาก – ราคาหลุด EMA และแนวรับย่อย, โครงสร้างราคาเป็น Lower Highs (LH) และ Lower Lows (LL), *Money Flow เป็นลบ (แรงขาย)* **โครงสร้างราคา (SMC):** * **TF Day:** ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS) * **TF4H:** ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS), มี Equal Highs (EQH) ที่เป็นแนวต้าน * **TF15:** บ่งบอกถึงแนวโน้มขาลงระยะสั้น (BOS ด้านล่าง, LH, LL), มี EQH เป็นแนวต้าน **Money Flow (LuxAlgo) - สรุป:** * **TF Day:** แรงซื้อยังคงแข็งแกร่งอย่างชัดเจน * **TF4H:** แรงซื้อเริ่มอ่อนแรงลง, มีแรงขายเข้ามา * **TF15:** แรงขายมีอิทธิพลเหนือกว่า  **EMA (Exponential Moving Average):** * **TF Day & 4H:** EMA 50 & 200 เป็นแนวรับสำคัญ * **TF15:** EMA 50 & 200 กลายเป็นแนวต้าน **แนวรับ-แนวต้านสำคัญ:** | Timeframe | แนวรับ | แนวต้าน | | :-------- | :------------------------------------------------------------------------- | :-------------------------------------------------------------- | | Day | EMA 50, EMA 200, 96,000-98,000, 85,724.7 | 109,998.9 (High เดิม) | | 4H | EMA 50, EMA 200, 96,000-98,000, 89,037.0 | 109,998.9 (EQH, High เดิม) | | 15m | 95,200 (Low ล่าสุด), 94,707.4 (Low ก่อนหน้า) | EMA 50, EMA 200, บริเวณ 96,000, 96,807.8, 97,000-97,200 | **กลยุทธ์ (BTCUSDT):** 1. **Buy on Dip (Day, 4H) - *มีความน่าเชื่อถือมากขึ้น แต่ยังคงต้องระมัดระวัง*:** * **เหตุผล:** แนวโน้มหลักยังเป็นขาขึ้น, Money Flow ใน TF Day แข็งแกร่ง * **เงื่อนไข:** *ยังคงต้องรอสัญญาณการกลับตัวของราคาใน TF15 ก่อน* (Breakout แนวต้านย่อย, Money Flow TF15 เป็นบวก, Bullish Candlestick Patterns) * **จุดเข้า (Day):** EMA 50, EMA 200, บริเวณ 96,000-98,000 * **จุดเข้า (4H):** EMA 50 * **Stop Loss:** ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ 2. **Short (15, ความเสี่ยงสูงมาก):** * **เหตุผล:** แนวโน้ม TF15 เป็นขาลง, Money Flow TF15 เป็นลบ * **เงื่อนไข:** ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้ * **จุดเข้า:** บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ * **Stop Loss:** เหนือ High ล่าสุดของ TF15 3. **Wait & See (ทางเลือกที่ปลอดภัย):** * **เหตุผล:** ความขัดแย้งระหว่าง Timeframes ยังคงมีอยู่ * รอให้ตลาดเฉลยทิศทางที่ชัดเจนกว่านี้ **คำแนะนำ (เน้นย้ำ):** * **Money Flow ใน TF Day:** เป็นปัจจัยบวกที่สำคัญ ทำให้กลยุทธ์ Buy on Dip มีน้ำหนักมากขึ้น * **ความขัดแย้งของ Timeframes:** ยังคงต้องระวัง TF15 ที่เป็นขาลง * **Volume:** การ Breakout/Breakdown ใดๆ ควรมี Volume สนับสนุน * **Risk Management:** สำคัญที่สุด **สรุป:** สถานการณ์ของ BTCUSDT โดยรวมยังคงเป็นบวก (ขาขึ้น) แต่มีความเสี่ยงในระยะสั้นจาก TF15 การตัดสินใจลงทุนควรพิจารณาจาก Timeframe ที่เหมาะสมกับสไตล์การเทรดของคุณ และอย่าลืมบริหารความเสี่ยงเสมอค่ะ **Disclaimer:** การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ @ cc8d072e:a6a026cb
2025-01-30 17:20:24Recently, I had the opportunity to work as an advisor for an AI agent project, which is created by team with a lot of fin-tech software develop experience. As we coded together, their real-time questions and challenges provided unique insights into the hurdles software engineers face when transitioning to AI development. They would pause at moments that most AI engineers take for granted - "How can we be sure the agent understood correctly?", "What if the model makes a mistake?", "How do we handle the uncertainty?" These weren't just isolated questions; they represented the fundamental paradigm shift required when moving from traditional software engineering to AI development. And thats why i think it might be worthy to take sometime write down this article and if you are going to start your first AI agent programming, spending 5 min reading t his will save you a lot of time later. ### 1. Shifting from Deterministic to Probabilistic Thinking - Traditional software engineering deals with deterministic outcomes - AI systems operate on probability rather than certainty - Engineers need to adapt from "100% correct" mindset to accepting probabilistic outcomes - Blockchain developers may find this particularly challenging due to their background in exact, deterministic systems ### 2. Understanding Core AI Concepts (There are a lot of concepts to understand, but i will focus on the most frequently asked ones) #### Memory Management - **Short-term Memory**: Implemented through conversation context - **Long-term Memory**: Implemented through vector databases (RAG - Retrieval Augmented Generation) - Context length management is crucial due to LLM token limitations #### Language Models and Fine-tuning - Base models (like GPT) provide general intelligence - Domain-specific knowledge can be added through: - Fine-tuning with custom datasets - Adding RAG layers for specific knowledge domains ### 3. Technical Framework Knowledge #### Essential Tools and Frameworks - Vercel AI SDK (if you are a typescript guy) - LangChain (alternative option) - Different models(openai, claude, gemini, etc, of course, now, deepseek. the temu in llm ) - Understanding of prompt engineering #### Multi-Agent Systems - Agents can communicate through natural language - Inter-agent communication requires careful system design - Implementation of thought processes and decision-making loops - Safety considerations for system commands and operations ### 4. Language and Localization Considerations - System prompts typically work best in English - Multi-language support requires careful handling: - Input translation to English - Processing in English - Output translation to target language - Model performance varies across different languages ### 5. Safety and Error Handling - Implementing validation layers for critical operations - Understanding model limitations and potential errors - Building feedback mechanisms to detect misunderstandings ## Conclusion Transitioning from software engineering to AI engineering requires a significant mindset shift. While traditional software engineering skills remain valuable, understanding probabilistic systems, language models, and AI-specific architectures is crucial. The key is to balance innovation with practical safety considerations, especially when dealing with critical applications. Remember that AI systems are not perfect, and building robust applications requires careful consideration of their limitations and appropriate safety measures. Start with existing frameworks and gradually build up complexity as you become more comfortable with AI-specific concepts and challenges.(the conclusion part is written by chatgpt, did you notice? :))
@ cc8d072e:a6a026cb
2025-01-30 17:20:24Recently, I had the opportunity to work as an advisor for an AI agent project, which is created by team with a lot of fin-tech software develop experience. As we coded together, their real-time questions and challenges provided unique insights into the hurdles software engineers face when transitioning to AI development. They would pause at moments that most AI engineers take for granted - "How can we be sure the agent understood correctly?", "What if the model makes a mistake?", "How do we handle the uncertainty?" These weren't just isolated questions; they represented the fundamental paradigm shift required when moving from traditional software engineering to AI development. And thats why i think it might be worthy to take sometime write down this article and if you are going to start your first AI agent programming, spending 5 min reading t his will save you a lot of time later. ### 1. Shifting from Deterministic to Probabilistic Thinking - Traditional software engineering deals with deterministic outcomes - AI systems operate on probability rather than certainty - Engineers need to adapt from "100% correct" mindset to accepting probabilistic outcomes - Blockchain developers may find this particularly challenging due to their background in exact, deterministic systems ### 2. Understanding Core AI Concepts (There are a lot of concepts to understand, but i will focus on the most frequently asked ones) #### Memory Management - **Short-term Memory**: Implemented through conversation context - **Long-term Memory**: Implemented through vector databases (RAG - Retrieval Augmented Generation) - Context length management is crucial due to LLM token limitations #### Language Models and Fine-tuning - Base models (like GPT) provide general intelligence - Domain-specific knowledge can be added through: - Fine-tuning with custom datasets - Adding RAG layers for specific knowledge domains ### 3. Technical Framework Knowledge #### Essential Tools and Frameworks - Vercel AI SDK (if you are a typescript guy) - LangChain (alternative option) - Different models(openai, claude, gemini, etc, of course, now, deepseek. the temu in llm ) - Understanding of prompt engineering #### Multi-Agent Systems - Agents can communicate through natural language - Inter-agent communication requires careful system design - Implementation of thought processes and decision-making loops - Safety considerations for system commands and operations ### 4. Language and Localization Considerations - System prompts typically work best in English - Multi-language support requires careful handling: - Input translation to English - Processing in English - Output translation to target language - Model performance varies across different languages ### 5. Safety and Error Handling - Implementing validation layers for critical operations - Understanding model limitations and potential errors - Building feedback mechanisms to detect misunderstandings ## Conclusion Transitioning from software engineering to AI engineering requires a significant mindset shift. While traditional software engineering skills remain valuable, understanding probabilistic systems, language models, and AI-specific architectures is crucial. The key is to balance innovation with practical safety considerations, especially when dealing with critical applications. Remember that AI systems are not perfect, and building robust applications requires careful consideration of their limitations and appropriate safety measures. Start with existing frameworks and gradually build up complexity as you become more comfortable with AI-specific concepts and challenges.(the conclusion part is written by chatgpt, did you notice? :)) @ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test. In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go. # It uses nostr The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol. Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key. In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along. In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim. # It leverages nostr Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app". This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back. Some examples might include: - Using nostr signers to encrypt or sign data, and then store that data on a proprietary server. - Using nostr relays as a kind of low-code backend, but using proprietary event payloads. - Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you. An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem. In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering. # It complements nostr Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role. One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense. Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)? A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs. To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen. # It embodies nostr Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate. This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product? To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the *protocol*, while apps that benefit nostr exclusively via network effect are integrated into nostr the *network*. An app that does both things is working in symbiosis with nostr as a whole. An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem: - In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors. - In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for. Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency _as nostr users_. If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states: > Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions. These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers. _As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria._ Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type". To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well, - There is a [spec](https://github.com/nostr-protocol/nips/pull/1190) for forms and responses, which means that... - Multiple clients can implement the same data format, allowing for credible exit and user choice, even of... - Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does... - Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to... - Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost". Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr. # It supports nostr Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually). This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content? In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together. A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own. So while I might hesitate to call many of these things "apps", they are certainly "nostr". # Appendix: it smells like a NINO So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr. You app might be a NINO if: - There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind) - There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository) - Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr - Your NIP relies on trusted third (or first) parties - There's only one implementation of your NIP (yours) - Your core value proposition doesn't depend on relays, events, or nostr identities - One or more relay urls are hard-coded into the source code - Your app depends on a specific relay implementation to work (*ahem*, relay29) - You don't validate event signatures - You don't publish events to relays you don't control - You don't read events from relays you don't control - You use legacy web services to solve problems, rather than nostr-native solutions - You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app - You don't use NIP 89 to discover clients and services - You haven't published a NIP 89 listing for your app - You don't leverage your users' web of trust for filtering out spam - You don't respect your users' mute lists - You try to "own" your users' data Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product. If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation: - Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine. - Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc. - Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats. - Think your idea is a good one? Talk to other devs or open a PR to the [nips repo](https://github.com/nostr-protocol/nips). No one can adopt your NIP if they don't know about it. - Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated. - Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask! I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test. In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go. # It uses nostr The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol. Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key. In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along. In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim. # It leverages nostr Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app". This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back. Some examples might include: - Using nostr signers to encrypt or sign data, and then store that data on a proprietary server. - Using nostr relays as a kind of low-code backend, but using proprietary event payloads. - Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you. An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem. In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering. # It complements nostr Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role. One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense. Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)? A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs. To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen. # It embodies nostr Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate. This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product? To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the *protocol*, while apps that benefit nostr exclusively via network effect are integrated into nostr the *network*. An app that does both things is working in symbiosis with nostr as a whole. An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem: - In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors. - In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for. Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency _as nostr users_. If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states: > Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions. These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers. _As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria._ Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type". To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well, - There is a [spec](https://github.com/nostr-protocol/nips/pull/1190) for forms and responses, which means that... - Multiple clients can implement the same data format, allowing for credible exit and user choice, even of... - Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does... - Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to... - Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost". Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr. # It supports nostr Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually). This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content? In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together. A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own. So while I might hesitate to call many of these things "apps", they are certainly "nostr". # Appendix: it smells like a NINO So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr. You app might be a NINO if: - There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind) - There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository) - Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr - Your NIP relies on trusted third (or first) parties - There's only one implementation of your NIP (yours) - Your core value proposition doesn't depend on relays, events, or nostr identities - One or more relay urls are hard-coded into the source code - Your app depends on a specific relay implementation to work (*ahem*, relay29) - You don't validate event signatures - You don't publish events to relays you don't control - You don't read events from relays you don't control - You use legacy web services to solve problems, rather than nostr-native solutions - You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app - You don't use NIP 89 to discover clients and services - You haven't published a NIP 89 listing for your app - You don't leverage your users' web of trust for filtering out spam - You don't respect your users' mute lists - You try to "own" your users' data Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product. If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation: - Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine. - Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc. - Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats. - Think your idea is a good one? Talk to other devs or open a PR to the [nips repo](https://github.com/nostr-protocol/nips). No one can adopt your NIP if they don't know about it. - Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated. - Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask! I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV. @ 2183e947:f497b975
2025-02-13 04:44:45# How Coinpools Improve Bitcoin # Problems with bitcoin UX problems with base layer payments include: - Mining fees are sometimes high - Confirmations usually take several minutes - Using it privately requires running a coinjoin server UX problems with lightning payments include: - Setup fees are sometimes high - Payments frequently fail - Payments aren't asynchronous (the recipient has to stand there with their device open waiting to do a revoke_and_ack on their old state -- unless they use a custodian) - Payments that *do* succeed occasionally take more than 30 seconds (due to stuck payments, automatic retries, and no ability to say "stop retrying" in any existing wallets that I'm aware of) - Using it privately requires manual channel management # Solutions A lot of my recent work focuses on non-interactive coinpools. I figured out a way to do them on bitcoin if we had CTV + CSFS, and then, with a bit more thought, I figured out that my model didn't actually require those things, so I am now working on an implementation. But my model does benefit a lot from CTV (less sure about CSFS at this point) so let me outline how non-interactive coinpools fix the above problems and along the way I will share how CTV specifically improves coinpools. ## "Mining fees are sometimes high" Coinpools improve the problem of "mining fees are sometimes high" by letting you bypass them in more cases. If you're in a coinpool and pay someone else in the same coinpool, your payment does not show up on the base layer, it just involves modifying some unilateral withdrawal transactions such that the sender can withdraw less and the recipient can withdraw more. The transactions are off-chain, like LN transactions, so you can do that without paying a base layer fee. ## "Confirmations usually take several minutes" Coinpools improve the problem of "confirmations usually take several minutes" in a similar manner. Payments *inside* a coinpool (i.e. to another pool user) merely involve modifying off-chain data (and revoking an old state), so they can be as fast as lightning. In most cases I expect them to be a bit faster because there's less need for pathfinding or negotiating with a variety of routing nodes. If the sender and the recipient are in the same pool, they only need to talk to each other and, in my model, a coordinator. ## "Using the base layer privately requires running a coinjoin server" Coinpools improve the problem of "using the base layer privately requires running a coinjoin server" in two ways: first, if you're in a coinpool and you send money to a bitcoin address, the blockchain doesn't know which coinpool user sent that payment. Analysts might be able to trace the payment to the coinpool, but from the blockchain's perspective, that's just a multisig; the actual person *inside* the multisig who sent the money is not revealed. However, my model uses a coordinator, and the coordinator probably knows which user sent the payment. Still, only 1 person knowing is better than having everyone on the blockchain know. Second, if you send money to someone *inside* the coinpool, in my model, the only people who know about your payment are the sender, the recipient, and the coordinator, and the recipient does not know who the sender is. Moreover, my model allows users to act as bridges from LN to other pool users, so even the coordinator doesn't know if the person who *looks* like the sender was the *real* sender or just a bridge node, with the *real* sender being someone on lightning. ## "Setup fees on lightning are sometimes high" Coinpools improve the problem of "setup fees are sometimes high" by having multiple users share the setup cost. My model allows a single bitcoin transaction to fund a coinpool with a number of members between 1 and probably about 100. (The max I've actually successfully tested is 11.) If the users share the cost of that transaction, then even in a high fee scenario, where bitcoin transactions cost $50, each user only has to pay a fraction of that, where the fraction is determined by how many users are joining the pool. If 10 people are joining, each user would pay $5 instead of $50. If 50 people are joining, each user would pay $1. If 100 people are joining, each user would pay 50¢. ## Sidebar: how CTV improves my coinpool model The setup is also where CTV greatly improves my model. For my model to work, the users have to coordinate to create the pool in something I call a "signing ceremony," which is very similar to a coinjoin. The signing ceremony has to be scheduled and each user has to show up for it or they won't get into the pool. With CTV, you could fix this: instead of a signing ceremony, an exchange could autosend your money into a coinpool on e.g. a monthly basis and email you the data you need to perform your unilateral exit. All they need from you is a pubkey, and they can do everything else. ## "Lightning payments frequently fail" Coinpools improve the problem of "payments frequently fail" by reducing the need for pathfinding, which is a typical cause of failure on lightning. If you are paying someone in the same pool as you, you always know an exact path: it will be you -> coordinator -> recipient. These short paths also reduce the likelihood of routing nodes having insufficient capacity to forward the payment. You've only got one "routing node" to worry about -- the coordinator. ## "Lightning payments aren't asynchronous" Coinpools *in general* don't improve the problem of "payments aren't asynchronous" but my model in particular *does* improve that problem because I am combining it with my hedgehog protocol from last year, which *does* allow for asynchronous lightning-like payments. Relatedly, my coinpool model technically has a network model, it's just a hub-and-spoke network: the coordinator is connected to every user of the pool and can forward asynchronous hedgehog payments to them. This means you can send money to someone when they are offline; they'll get it whenever they *do* get online, even if *you* went offline in the meantime. ## "Lightning payments sometimes take too long" Coinpools improve the problem of "stuck" lightning payments by reducing the number of hops along the route. As above, a payment inside the pool (per my model) is always just sender -> coordinator -> recipient. Due to only having 1 hop, there are fewer opportunities for a node to have a network issue and cause a delay. ## "Channel management is a pain" Coinpools have multiple ways of improving the problem of manual channel management. In particular, not all coinpool models *have* channels, so channel management is not always needed in a coinpool. My model, however, does have channels, so channel management is still a thing. Nonetheless, my model improves channel management in two ways: first, the setup costs are lower for the reasons given above. Second, payment asynchronicity helps for the following reason: The worst pain point in channel management *today* occurs when someone sends you a payment but it fails because you didn't have enough inbound capacity. That doesn't happen in my coinpool model because payments are asynchronous. If you don't have enough inbound capacity, the payment doesn't fail, it just remains pending. So all you have to do is open a new channel (i.e. enter a new pool) and *then* finalize the payment. ## Zap me I hope this essay clarifies why coinpools improve the problems I outlined and why CTV improves coinpools. I also hope this gets you a bit excited for my latest coinpool invention, which I hope to release soon :D (It really is very close to demo-ready.) If you liked this essay, consider zapping me: supertestnet@coinos.io
@ 2183e947:f497b975
2025-02-13 04:44:45# How Coinpools Improve Bitcoin # Problems with bitcoin UX problems with base layer payments include: - Mining fees are sometimes high - Confirmations usually take several minutes - Using it privately requires running a coinjoin server UX problems with lightning payments include: - Setup fees are sometimes high - Payments frequently fail - Payments aren't asynchronous (the recipient has to stand there with their device open waiting to do a revoke_and_ack on their old state -- unless they use a custodian) - Payments that *do* succeed occasionally take more than 30 seconds (due to stuck payments, automatic retries, and no ability to say "stop retrying" in any existing wallets that I'm aware of) - Using it privately requires manual channel management # Solutions A lot of my recent work focuses on non-interactive coinpools. I figured out a way to do them on bitcoin if we had CTV + CSFS, and then, with a bit more thought, I figured out that my model didn't actually require those things, so I am now working on an implementation. But my model does benefit a lot from CTV (less sure about CSFS at this point) so let me outline how non-interactive coinpools fix the above problems and along the way I will share how CTV specifically improves coinpools. ## "Mining fees are sometimes high" Coinpools improve the problem of "mining fees are sometimes high" by letting you bypass them in more cases. If you're in a coinpool and pay someone else in the same coinpool, your payment does not show up on the base layer, it just involves modifying some unilateral withdrawal transactions such that the sender can withdraw less and the recipient can withdraw more. The transactions are off-chain, like LN transactions, so you can do that without paying a base layer fee. ## "Confirmations usually take several minutes" Coinpools improve the problem of "confirmations usually take several minutes" in a similar manner. Payments *inside* a coinpool (i.e. to another pool user) merely involve modifying off-chain data (and revoking an old state), so they can be as fast as lightning. In most cases I expect them to be a bit faster because there's less need for pathfinding or negotiating with a variety of routing nodes. If the sender and the recipient are in the same pool, they only need to talk to each other and, in my model, a coordinator. ## "Using the base layer privately requires running a coinjoin server" Coinpools improve the problem of "using the base layer privately requires running a coinjoin server" in two ways: first, if you're in a coinpool and you send money to a bitcoin address, the blockchain doesn't know which coinpool user sent that payment. Analysts might be able to trace the payment to the coinpool, but from the blockchain's perspective, that's just a multisig; the actual person *inside* the multisig who sent the money is not revealed. However, my model uses a coordinator, and the coordinator probably knows which user sent the payment. Still, only 1 person knowing is better than having everyone on the blockchain know. Second, if you send money to someone *inside* the coinpool, in my model, the only people who know about your payment are the sender, the recipient, and the coordinator, and the recipient does not know who the sender is. Moreover, my model allows users to act as bridges from LN to other pool users, so even the coordinator doesn't know if the person who *looks* like the sender was the *real* sender or just a bridge node, with the *real* sender being someone on lightning. ## "Setup fees on lightning are sometimes high" Coinpools improve the problem of "setup fees are sometimes high" by having multiple users share the setup cost. My model allows a single bitcoin transaction to fund a coinpool with a number of members between 1 and probably about 100. (The max I've actually successfully tested is 11.) If the users share the cost of that transaction, then even in a high fee scenario, where bitcoin transactions cost $50, each user only has to pay a fraction of that, where the fraction is determined by how many users are joining the pool. If 10 people are joining, each user would pay $5 instead of $50. If 50 people are joining, each user would pay $1. If 100 people are joining, each user would pay 50¢. ## Sidebar: how CTV improves my coinpool model The setup is also where CTV greatly improves my model. For my model to work, the users have to coordinate to create the pool in something I call a "signing ceremony," which is very similar to a coinjoin. The signing ceremony has to be scheduled and each user has to show up for it or they won't get into the pool. With CTV, you could fix this: instead of a signing ceremony, an exchange could autosend your money into a coinpool on e.g. a monthly basis and email you the data you need to perform your unilateral exit. All they need from you is a pubkey, and they can do everything else. ## "Lightning payments frequently fail" Coinpools improve the problem of "payments frequently fail" by reducing the need for pathfinding, which is a typical cause of failure on lightning. If you are paying someone in the same pool as you, you always know an exact path: it will be you -> coordinator -> recipient. These short paths also reduce the likelihood of routing nodes having insufficient capacity to forward the payment. You've only got one "routing node" to worry about -- the coordinator. ## "Lightning payments aren't asynchronous" Coinpools *in general* don't improve the problem of "payments aren't asynchronous" but my model in particular *does* improve that problem because I am combining it with my hedgehog protocol from last year, which *does* allow for asynchronous lightning-like payments. Relatedly, my coinpool model technically has a network model, it's just a hub-and-spoke network: the coordinator is connected to every user of the pool and can forward asynchronous hedgehog payments to them. This means you can send money to someone when they are offline; they'll get it whenever they *do* get online, even if *you* went offline in the meantime. ## "Lightning payments sometimes take too long" Coinpools improve the problem of "stuck" lightning payments by reducing the number of hops along the route. As above, a payment inside the pool (per my model) is always just sender -> coordinator -> recipient. Due to only having 1 hop, there are fewer opportunities for a node to have a network issue and cause a delay. ## "Channel management is a pain" Coinpools have multiple ways of improving the problem of manual channel management. In particular, not all coinpool models *have* channels, so channel management is not always needed in a coinpool. My model, however, does have channels, so channel management is still a thing. Nonetheless, my model improves channel management in two ways: first, the setup costs are lower for the reasons given above. Second, payment asynchronicity helps for the following reason: The worst pain point in channel management *today* occurs when someone sends you a payment but it fails because you didn't have enough inbound capacity. That doesn't happen in my coinpool model because payments are asynchronous. If you don't have enough inbound capacity, the payment doesn't fail, it just remains pending. So all you have to do is open a new channel (i.e. enter a new pool) and *then* finalize the payment. ## Zap me I hope this essay clarifies why coinpools improve the problems I outlined and why CTV improves coinpools. I also hope this gets you a bit excited for my latest coinpool invention, which I hope to release soon :D (It really is very close to demo-ready.) If you liked this essay, consider zapping me: supertestnet@coinos.io @ f1989a96:bcaaf2c1
2025-01-30 15:25:34Good morning, readers! This week, authoritarian regimes augmented their control and monitoring of online spaces in an attempt to suppress the dissenting voices of those they have financially repressed. While Pakistanis grapple with the highest cost of living in Asia, the military-backed regime passed an oppressive social media bill that empowers the government to imprison and fine individuals deemed to be spreading “disinformation” online.\ \ Meanwhile, in Belarus, authoritarian Alexander Lukashenko secured a seventh term in an openly rigged presidential election, further consolidating his grip on power and deepening the country’s political and financial repression. This prolongs his rule beyond three decades, cementing him as the sole ruler of Belarus since the country gained independence from the Soviet Union in 1991. In freedom technology news, open-source developer Super Testnet released a new privacy tool called Hurricash. It lets multiple users lock funds together in a single Bitcoin Unspent Transaction Output (UTXO), allowing them to transact within the pool of users with greater privacy and efficiency. With greater liquidity and adoption, it could prove a useful tool for human rights activists seeking financial privacy. \ \ Additionally, Zaprite integrated BTCPay Server, enabling users to accept Bitcoin, Lightning, and fiat payments using self-custodial and self-hosted Bitcoin infrastructure. This is particularly valuable for nonprofits and activists in authoritarian regimes, where governments monitor and restrict financial activity. We end with the latest episode of the “Money Matters” podcast, where Jack Mallers, CEO of Strike, interviews HRF Chief Strategy Officer Alex Gladstein to discuss the often overlooked connection between Bitcoin and financial freedom. **Now, let’s jump right in!** ### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Belarus | Lukashenko Sweeps Openly Rigged Election Amid Financial Repression** In Belarus, authoritarian leader Alexander Lukashenko [secured](https://www.newarab.com/news/belarus-lukashenko-extends-three-decade-rule-sham-election) a seventh term in an openly rigged presidential election. Lukashenko’s crusade against dissent and political opposition has left many citizens and opposition figures exiled, imprisoned, and financially repressed. Historically, his regime has frozen bank accounts, blocked foreign currency exchanges, and cut off independent media from funding. By wielding financial and political power, Lukashenko ensures that no real opposition can rise, turning Belarus into a country where even the illusion of democracy has disappeared. In these environments, Bitcoin and tools like [Lnp2pbot](https://lnp2pbot.com) (an HRF grantee) help Belarusians circumvent financial restrictions and transact in a currency that Lukashenko can’t control. #### **Nigeria | Joins BRICS Economic Coalition** Nigeria is expanding its financial repression both internationally and domestically. It recently [joined](https://archive.ph/ZQDlO) BRICS, an intergovernmental economic organization led by the Chinese and Russian regimes. For some, this raises concerns as Nigeria may deepen its authoritarian ways and further restrict individual financial freedoms. Member countries are each leaders in the development and implementation of central bank digital currencies (CBDCs), threatening individual financial autonomy as financial control is increasingly placed under the purview of authoritarian states. In parallel, the Nigerian regime plans to [distribute](https://nairametrics.com/2025/01/15/fg-to-distribute-n75000-cash-transfers-to-70-million-nigerians-by-2025/) a 75,000 naira ($48) “cash transfer” to the nation’s poorest citizens. This bid to alleviate poverty risks, while stoking inflation and compromising privacy, as the initiative relies on digital registration through the National Identity Number (NIN) system. Nigeria’s strategy of using both micro and macro financial controls limits open markets and curtails individual freedoms. #### **Pakistan | Regime Passes Repressive Bill Targeting Online Spaces** Pakistan’s military-backed regime [passed](https://apnews.com/article/pakistan-cyber-law-social-media-6de3a878c434abb154b91012bc9ca33c) a repressive social media bill that allows officials to imprison citizens for spreading “disinformation” online. Under this new law, officials can block “unlawful and offensive” content and remove users from social media at a time when Pakistanis are increasingly turning to online spaces to express discontent over regime-imposed economic hardships. Those “spreading disinformation” risk facing three years in prison and fines of up to 2 million rupees ($7,150) — a harsh penalty for citizens grappling with the [highest](https://www.firstpost.com/world/pakistan-tops-asia-in-living-costs-and-inflation-rates-report-reveals-13759245.html) cost of living on the continent. Further, social platforms must register with the Social Media Protection and Regulatory Authority to operate or risk a permanent ban. Censorship and Internet controls are sadly nothing new for Pakistanis since the regime has [blocked](https://timesofindia.indiatimes.com/world/pakistan/social-media-platform-x-shutdown-continues-for-eighth-day-in-pakistan/articleshow/107983076.cms) X during elections and enacted a nationwide [Internet firewall](https://www.aljazeera.com/news/2024/11/26/pakistan-tests-china-like-digital-firewall-to-tighten-online-surveillance) to suppress public discourse and action. #### **Cuba | Salary of Baseball Player Buys a Carton of Eggs** Cuba’s cost-of-living crisis is so [severe](https://havanatimes.org/cuba/the-salary-of-a-cuban-baseball-player-buys-a-carton-of-eggs/) that even the country’s top and most profitable athletes cannot make ends meet. Exemplifying this, the monthly salary of a professional baseball player in the National Series — Cuba’s premier sporting event — barely covers the cost of a carton of eggs, forcing them to [seek opportunities](https://www.reuters.com/world/americas/cubas-migratory-stampede-has-no-end-sight-2024-09-11/) elsewhere. With the Cuban peso in freefall, [several](https://havanatimes.org/cuba/the-salary-of-a-cuban-baseball-player-buys-a-carton-of-eggs/) players have resigned, citing financial hardships as the reason for leaving the sport they love. Their departures reflect a broader reality: wages across Cuba fail to keep pace with severe inflation caused by the Cuban regime’s continuous economic mismanagement. The state continues to enforce wages in the collapsing peso while requiring “MLC” credits to purchase high-quality food and goods in a system that pulls in foreign exchange from abroad while stealing from citizens at home. #### **South Sudan | Regime Blocks Citizen Access to Social Media** In South Sudan, rebel leader Salva Kiir Mayardit [directed](https://nation.africa/kenya/news/africa/south-sudan-shuts-down-social-media-for-three-months-4898628) the National Communication Authority (NCA) to block each citizen’s access to social media nationwide for up to three months, citing concerns over “public safety” and “mental health.” This decision follows violent videos of Sudanese armed forces attacking South Sudanese refugees in Sudan. Sudanese rights groups condemned the ban as a blatant act of censorship and an abuse of power. “The death of our South Sudanese in Sudan should not culminate in blocking social media, which is one of the ways many of us get information,” [said](https://nation.africa/kenya/news/africa/south-sudan-shuts-down-social-media-for-three-months-4898628) one Sudanese citizen. By restricting social media, the regime demonstrates a clear willingness to silence dissent, suppress information, and stifle transparency under the guise of “protection.” As Sudanese grapple with [rising](https://www.bloomberg.com/news/articles/2024-03-30/south-sudan-cracks-down-on-parallel-fx-market-to-fight-inflation?utm_campaign=socialflow-organic&utm_source=twitter&utm_medium=social&cmpid%3D=socialflow-twitter-africa&utm_content=africa) prices, the ban further isolates them, leaving little room to coordinate relief efforts, share grievances, or hold those in power accountable. ## RECOMMENDED CONTENT #### **IMF Offers a Glimpse at the Perils of Central Bank Digital Currencies by J.D. Tuccille** In this [article](https://reason.com/2024/12/18/imf-offers-a-glimpse-at-the-perils-of-central-bank-digital-currencies/) for [Reason Magazine](https://reason.com/), [J.D. Tuccille](https://x.com/JD_Tuccille) examines the dangers of central bank digital currencies (CBDCs) and their implications for financial independence and privacy. Drawing from the International Monetary Fund’s (IMF) “[CBDC Virtual Handbook](https://www.imf.org/en/Topics/fintech/central-bank-digital-currency/virtual-handbook),” Tuccille explains how CBDCs grant governments unprecedented control to monitor transactions, impose restrictions, and manipulate financial behavior. He contrasts these state-issued digital currencies with decentralized alternatives like Bitcoin, highlighting the stark differences in privacy and user freedom. You can read the complete analysis [here](https://reason.com/2024/12/18/imf-offers-a-glimpse-at-the-perils-of-central-bank-digital-currencies/). To learn more about CBDCs and the threats they pose to civil liberties and human rights, check out our [HRF’s CBDC Tracker](https://cbdctracker.hrf.org/). ## BITCOIN AND FREEDOM TECH NEWS #### **Super Testnet | Launches Hurricash** Bitcoin Developer [Super Testnet](https://github.com/supertestnet) released [Hurricash](https://github.com/supertestnet/hurricash), an experimental and open-source Bitcoin privacy protocol. Hurricash lets multiple users lock funds together in a single Bitcoin [Unspent Transaction Output](https://river.com/learn/bitcoins-utxo-model/) (UTXO), making their transactions more private. Users can then transact within the pool with greater efficiency and privacy. With greater liquidity and adoption, it could prove a useful tool for human rights defenders seeking financial privacy. Innovations like this could also pave the way for activists in many decades to afford trustless BTC transactions. #### **Zaprite | Integrates BTCPay Server** [Zaprite](https://zaprite.com/), a platform for accepting Bitcoin payments, recently [integrated](https://blog.zaprite.com/how-to-connect-btcpay-server/) [BTCPay Server](https://btcpayserver.org/), an open-source Bitcoin payment processor and HRF grantee. This integration allows users to accept Bitcoin, Lightning, and fiat payments (like USD) while maintaining full control over their funds — something Zaprite couldn’t afford on its own. By connecting with BTCPay Server, users can receive Bitcoin payments directly to their own self-hosted wallet and node, reducing censorship risks and enhancing financial independence. This is valuable for nonprofits, merchants, and activists in authoritarian regimes, where governments monitor, freeze, and restrict financial activity. #### **Breez SDK | Implements Pay to BIP 353 Addresses** The Breez Software Development Kit (SDK), a tool for integrating self-custodial Lightning payments into apps and services, now [supports](https://github.com/breez/breez-sdk-liquid/releases/tag/0.6.2) payments to [BIP 353](https://github.com/bitcoin/bips/blob/master/bip-0353.mediawiki) addresses. BIP 353 enables individuals with access to a domain the ability to create static, human-readable payment addresses (such as user@domain), instead of a long string of letters and numbers. This means an activist with a website can receive Bitcoin donations directly through their domain — if their wallet supports BIP 353. Several Bitcoin wallets already using the Breez SDK include [Cake Wallet](https://cakewallet.com/), [Blitz Wallet](https://blitz-wallet.com/), and [Klever Wallet](https://klever.io/). These static addresses make receiving Bitcoin easier, more private, and more censorship resistant, reducing surveillance risks and simplifying recurring payments. #### **Ark Labs | Releases Wallet Software Development Kit** [Ark](https://arklabs.to/), a protocol promising faster and cheaper transactions on Bitcoin, [released](https://blog.arklabs.to/introducing-the-ark-wallet-sdk-d1c77ce61cfc) a wallet software development kit (SDK). The SDK is aimed at helping developers more readily create Ark-compatible Bitcoin wallets that support both traditional Bitcoin payments and Ark’s instant transactions on mobile and desktop platforms. Protocols like Ark hold promise for greater transaction efficiency and improve its transaction capabilities for those who need it most. #### **Tornado Cash | US District Court Reverses Sanctions** A United States District Court [ruled](https://www.theblock.co/post/336319/us-court-rules-against-tornado-cash-sanctions-torn-cryptocurrency-surges-140) to reverse the sanctions on Tornado Cash, marking a major legal win for financial privacy in the digital asset space. This decision follows a previous Appeals Court [ruling](https://www.therage.co/fifth-circuit-lifts-tornado-cash-sanctions/?mc_cid=2d0b2336ed&mc_eid=8de40cf474) that found the Treasury overstepped its authority by sentencing the digital asset mixer under the International Emergency Economic Powers Act (IEEPA). The court determined that Tornado Cash’s smart contracts (self-executing lines of code) do not constitute “property,” making them ineligible for sanctions under existing laws. These rulings set a positive precedent for decentralized protocols and financial privacy in a world where these tools are desperately needed. Developers cannot work on privacy openly in dictatorships, so they need havens in liberal democracies. #### **OpenSats | Announces Grants for Three Bitcoin Core Contributors** OpenSats, a public nonprofit supporting open-source software and projects, [announced](https://opensats.org/blog/more-for-core) three new grants for Bitcoin Core contributors [L0rinc](https://github.com/l0rinc), [kevkevin](https://github.com/kevkevinpal), and [Daniela Brozzoni](https://github.com/danielabrozzoni). L0rinc will improve Bitcoin Core's performance and reliability by optimizing Initial Block Download (IBD), block storage, and database functionality. Kevkevin will enhance Bitcoin Core's stability, security, and usability by fixing bugs and reviewing pull requests. Finally, Daniela will review Bitcoin Core's code, adding features and improving test coverage. HRF is pleased to see the continued support of open-source developers from this [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) grantee. #### **Bitcoin Chiang Mai | Bitcoin for Human Rights Meetup** [Bitcoin Chiang Mai](https://www.bitcoinchiangmai.org/), a grassroots Bitcoin community in Thailand, will host a meetup [exploring](https://x.com/jimmykostro/status/1883393135436529844?s=46) Bitcoin’s role in human rights and financial freedom on Feb. 7, 2025. HRF Global Bitcoin Adoption Fellow Win Ko Ko Aung will discuss how Bitcoin empowers activists and communities under authoritarian rule, with a particular focus on Burmese citizens. Held in Burmese and English, the event will educate attendees on Bitcoin as a tool for escaping financial repression. If you have Burmese friends in Chiang Mai, share this opportunity with them. You can register [here](https://docs.google.com/forms/d/e/1FAIpQLScscuPhxba_Ma040Wwm9-ud7eODWVMpb_8RpFx-12yYbvfl5g/viewform). ## RECOMMENDED CONTENT #### **Bitcoin and Freedom with Alex Gladstein** In a special [episode](https://www.youtube.com/watch?v=hC93o30gUa8) of the “Money Matters” podcast, Jack Mallers, CEO of Strike, speaks with Alex Gladstein, chief strategy officer at HRF, to discuss the powerful link between Bitcoin and financial freedom. Gladstein unpacks how authoritarian regimes manipulate money to control the public and explains why open-source financial tools are critical for resisting oppression. His insights make a compelling case for financial sovereignty as a fundamental human right — and why Bitcoin remains the most effective tool to secure it. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/)
@ f1989a96:bcaaf2c1
2025-01-30 15:25:34Good morning, readers! This week, authoritarian regimes augmented their control and monitoring of online spaces in an attempt to suppress the dissenting voices of those they have financially repressed. While Pakistanis grapple with the highest cost of living in Asia, the military-backed regime passed an oppressive social media bill that empowers the government to imprison and fine individuals deemed to be spreading “disinformation” online.\ \ Meanwhile, in Belarus, authoritarian Alexander Lukashenko secured a seventh term in an openly rigged presidential election, further consolidating his grip on power and deepening the country’s political and financial repression. This prolongs his rule beyond three decades, cementing him as the sole ruler of Belarus since the country gained independence from the Soviet Union in 1991. In freedom technology news, open-source developer Super Testnet released a new privacy tool called Hurricash. It lets multiple users lock funds together in a single Bitcoin Unspent Transaction Output (UTXO), allowing them to transact within the pool of users with greater privacy and efficiency. With greater liquidity and adoption, it could prove a useful tool for human rights activists seeking financial privacy. \ \ Additionally, Zaprite integrated BTCPay Server, enabling users to accept Bitcoin, Lightning, and fiat payments using self-custodial and self-hosted Bitcoin infrastructure. This is particularly valuable for nonprofits and activists in authoritarian regimes, where governments monitor and restrict financial activity. We end with the latest episode of the “Money Matters” podcast, where Jack Mallers, CEO of Strike, interviews HRF Chief Strategy Officer Alex Gladstein to discuss the often overlooked connection between Bitcoin and financial freedom. **Now, let’s jump right in!** ### [**Subscribe Here**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Belarus | Lukashenko Sweeps Openly Rigged Election Amid Financial Repression** In Belarus, authoritarian leader Alexander Lukashenko [secured](https://www.newarab.com/news/belarus-lukashenko-extends-three-decade-rule-sham-election) a seventh term in an openly rigged presidential election. Lukashenko’s crusade against dissent and political opposition has left many citizens and opposition figures exiled, imprisoned, and financially repressed. Historically, his regime has frozen bank accounts, blocked foreign currency exchanges, and cut off independent media from funding. By wielding financial and political power, Lukashenko ensures that no real opposition can rise, turning Belarus into a country where even the illusion of democracy has disappeared. In these environments, Bitcoin and tools like [Lnp2pbot](https://lnp2pbot.com) (an HRF grantee) help Belarusians circumvent financial restrictions and transact in a currency that Lukashenko can’t control. #### **Nigeria | Joins BRICS Economic Coalition** Nigeria is expanding its financial repression both internationally and domestically. It recently [joined](https://archive.ph/ZQDlO) BRICS, an intergovernmental economic organization led by the Chinese and Russian regimes. For some, this raises concerns as Nigeria may deepen its authoritarian ways and further restrict individual financial freedoms. Member countries are each leaders in the development and implementation of central bank digital currencies (CBDCs), threatening individual financial autonomy as financial control is increasingly placed under the purview of authoritarian states. In parallel, the Nigerian regime plans to [distribute](https://nairametrics.com/2025/01/15/fg-to-distribute-n75000-cash-transfers-to-70-million-nigerians-by-2025/) a 75,000 naira ($48) “cash transfer” to the nation’s poorest citizens. This bid to alleviate poverty risks, while stoking inflation and compromising privacy, as the initiative relies on digital registration through the National Identity Number (NIN) system. Nigeria’s strategy of using both micro and macro financial controls limits open markets and curtails individual freedoms. #### **Pakistan | Regime Passes Repressive Bill Targeting Online Spaces** Pakistan’s military-backed regime [passed](https://apnews.com/article/pakistan-cyber-law-social-media-6de3a878c434abb154b91012bc9ca33c) a repressive social media bill that allows officials to imprison citizens for spreading “disinformation” online. Under this new law, officials can block “unlawful and offensive” content and remove users from social media at a time when Pakistanis are increasingly turning to online spaces to express discontent over regime-imposed economic hardships. Those “spreading disinformation” risk facing three years in prison and fines of up to 2 million rupees ($7,150) — a harsh penalty for citizens grappling with the [highest](https://www.firstpost.com/world/pakistan-tops-asia-in-living-costs-and-inflation-rates-report-reveals-13759245.html) cost of living on the continent. Further, social platforms must register with the Social Media Protection and Regulatory Authority to operate or risk a permanent ban. Censorship and Internet controls are sadly nothing new for Pakistanis since the regime has [blocked](https://timesofindia.indiatimes.com/world/pakistan/social-media-platform-x-shutdown-continues-for-eighth-day-in-pakistan/articleshow/107983076.cms) X during elections and enacted a nationwide [Internet firewall](https://www.aljazeera.com/news/2024/11/26/pakistan-tests-china-like-digital-firewall-to-tighten-online-surveillance) to suppress public discourse and action. #### **Cuba | Salary of Baseball Player Buys a Carton of Eggs** Cuba’s cost-of-living crisis is so [severe](https://havanatimes.org/cuba/the-salary-of-a-cuban-baseball-player-buys-a-carton-of-eggs/) that even the country’s top and most profitable athletes cannot make ends meet. Exemplifying this, the monthly salary of a professional baseball player in the National Series — Cuba’s premier sporting event — barely covers the cost of a carton of eggs, forcing them to [seek opportunities](https://www.reuters.com/world/americas/cubas-migratory-stampede-has-no-end-sight-2024-09-11/) elsewhere. With the Cuban peso in freefall, [several](https://havanatimes.org/cuba/the-salary-of-a-cuban-baseball-player-buys-a-carton-of-eggs/) players have resigned, citing financial hardships as the reason for leaving the sport they love. Their departures reflect a broader reality: wages across Cuba fail to keep pace with severe inflation caused by the Cuban regime’s continuous economic mismanagement. The state continues to enforce wages in the collapsing peso while requiring “MLC” credits to purchase high-quality food and goods in a system that pulls in foreign exchange from abroad while stealing from citizens at home. #### **South Sudan | Regime Blocks Citizen Access to Social Media** In South Sudan, rebel leader Salva Kiir Mayardit [directed](https://nation.africa/kenya/news/africa/south-sudan-shuts-down-social-media-for-three-months-4898628) the National Communication Authority (NCA) to block each citizen’s access to social media nationwide for up to three months, citing concerns over “public safety” and “mental health.” This decision follows violent videos of Sudanese armed forces attacking South Sudanese refugees in Sudan. Sudanese rights groups condemned the ban as a blatant act of censorship and an abuse of power. “The death of our South Sudanese in Sudan should not culminate in blocking social media, which is one of the ways many of us get information,” [said](https://nation.africa/kenya/news/africa/south-sudan-shuts-down-social-media-for-three-months-4898628) one Sudanese citizen. By restricting social media, the regime demonstrates a clear willingness to silence dissent, suppress information, and stifle transparency under the guise of “protection.” As Sudanese grapple with [rising](https://www.bloomberg.com/news/articles/2024-03-30/south-sudan-cracks-down-on-parallel-fx-market-to-fight-inflation?utm_campaign=socialflow-organic&utm_source=twitter&utm_medium=social&cmpid%3D=socialflow-twitter-africa&utm_content=africa) prices, the ban further isolates them, leaving little room to coordinate relief efforts, share grievances, or hold those in power accountable. ## RECOMMENDED CONTENT #### **IMF Offers a Glimpse at the Perils of Central Bank Digital Currencies by J.D. Tuccille** In this [article](https://reason.com/2024/12/18/imf-offers-a-glimpse-at-the-perils-of-central-bank-digital-currencies/) for [Reason Magazine](https://reason.com/), [J.D. Tuccille](https://x.com/JD_Tuccille) examines the dangers of central bank digital currencies (CBDCs) and their implications for financial independence and privacy. Drawing from the International Monetary Fund’s (IMF) “[CBDC Virtual Handbook](https://www.imf.org/en/Topics/fintech/central-bank-digital-currency/virtual-handbook),” Tuccille explains how CBDCs grant governments unprecedented control to monitor transactions, impose restrictions, and manipulate financial behavior. He contrasts these state-issued digital currencies with decentralized alternatives like Bitcoin, highlighting the stark differences in privacy and user freedom. You can read the complete analysis [here](https://reason.com/2024/12/18/imf-offers-a-glimpse-at-the-perils-of-central-bank-digital-currencies/). To learn more about CBDCs and the threats they pose to civil liberties and human rights, check out our [HRF’s CBDC Tracker](https://cbdctracker.hrf.org/). ## BITCOIN AND FREEDOM TECH NEWS #### **Super Testnet | Launches Hurricash** Bitcoin Developer [Super Testnet](https://github.com/supertestnet) released [Hurricash](https://github.com/supertestnet/hurricash), an experimental and open-source Bitcoin privacy protocol. Hurricash lets multiple users lock funds together in a single Bitcoin [Unspent Transaction Output](https://river.com/learn/bitcoins-utxo-model/) (UTXO), making their transactions more private. Users can then transact within the pool with greater efficiency and privacy. With greater liquidity and adoption, it could prove a useful tool for human rights defenders seeking financial privacy. Innovations like this could also pave the way for activists in many decades to afford trustless BTC transactions. #### **Zaprite | Integrates BTCPay Server** [Zaprite](https://zaprite.com/), a platform for accepting Bitcoin payments, recently [integrated](https://blog.zaprite.com/how-to-connect-btcpay-server/) [BTCPay Server](https://btcpayserver.org/), an open-source Bitcoin payment processor and HRF grantee. This integration allows users to accept Bitcoin, Lightning, and fiat payments (like USD) while maintaining full control over their funds — something Zaprite couldn’t afford on its own. By connecting with BTCPay Server, users can receive Bitcoin payments directly to their own self-hosted wallet and node, reducing censorship risks and enhancing financial independence. This is valuable for nonprofits, merchants, and activists in authoritarian regimes, where governments monitor, freeze, and restrict financial activity. #### **Breez SDK | Implements Pay to BIP 353 Addresses** The Breez Software Development Kit (SDK), a tool for integrating self-custodial Lightning payments into apps and services, now [supports](https://github.com/breez/breez-sdk-liquid/releases/tag/0.6.2) payments to [BIP 353](https://github.com/bitcoin/bips/blob/master/bip-0353.mediawiki) addresses. BIP 353 enables individuals with access to a domain the ability to create static, human-readable payment addresses (such as user@domain), instead of a long string of letters and numbers. This means an activist with a website can receive Bitcoin donations directly through their domain — if their wallet supports BIP 353. Several Bitcoin wallets already using the Breez SDK include [Cake Wallet](https://cakewallet.com/), [Blitz Wallet](https://blitz-wallet.com/), and [Klever Wallet](https://klever.io/). These static addresses make receiving Bitcoin easier, more private, and more censorship resistant, reducing surveillance risks and simplifying recurring payments. #### **Ark Labs | Releases Wallet Software Development Kit** [Ark](https://arklabs.to/), a protocol promising faster and cheaper transactions on Bitcoin, [released](https://blog.arklabs.to/introducing-the-ark-wallet-sdk-d1c77ce61cfc) a wallet software development kit (SDK). The SDK is aimed at helping developers more readily create Ark-compatible Bitcoin wallets that support both traditional Bitcoin payments and Ark’s instant transactions on mobile and desktop platforms. Protocols like Ark hold promise for greater transaction efficiency and improve its transaction capabilities for those who need it most. #### **Tornado Cash | US District Court Reverses Sanctions** A United States District Court [ruled](https://www.theblock.co/post/336319/us-court-rules-against-tornado-cash-sanctions-torn-cryptocurrency-surges-140) to reverse the sanctions on Tornado Cash, marking a major legal win for financial privacy in the digital asset space. This decision follows a previous Appeals Court [ruling](https://www.therage.co/fifth-circuit-lifts-tornado-cash-sanctions/?mc_cid=2d0b2336ed&mc_eid=8de40cf474) that found the Treasury overstepped its authority by sentencing the digital asset mixer under the International Emergency Economic Powers Act (IEEPA). The court determined that Tornado Cash’s smart contracts (self-executing lines of code) do not constitute “property,” making them ineligible for sanctions under existing laws. These rulings set a positive precedent for decentralized protocols and financial privacy in a world where these tools are desperately needed. Developers cannot work on privacy openly in dictatorships, so they need havens in liberal democracies. #### **OpenSats | Announces Grants for Three Bitcoin Core Contributors** OpenSats, a public nonprofit supporting open-source software and projects, [announced](https://opensats.org/blog/more-for-core) three new grants for Bitcoin Core contributors [L0rinc](https://github.com/l0rinc), [kevkevin](https://github.com/kevkevinpal), and [Daniela Brozzoni](https://github.com/danielabrozzoni). L0rinc will improve Bitcoin Core's performance and reliability by optimizing Initial Block Download (IBD), block storage, and database functionality. Kevkevin will enhance Bitcoin Core's stability, security, and usability by fixing bugs and reviewing pull requests. Finally, Daniela will review Bitcoin Core's code, adding features and improving test coverage. HRF is pleased to see the continued support of open-source developers from this [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) grantee. #### **Bitcoin Chiang Mai | Bitcoin for Human Rights Meetup** [Bitcoin Chiang Mai](https://www.bitcoinchiangmai.org/), a grassroots Bitcoin community in Thailand, will host a meetup [exploring](https://x.com/jimmykostro/status/1883393135436529844?s=46) Bitcoin’s role in human rights and financial freedom on Feb. 7, 2025. HRF Global Bitcoin Adoption Fellow Win Ko Ko Aung will discuss how Bitcoin empowers activists and communities under authoritarian rule, with a particular focus on Burmese citizens. Held in Burmese and English, the event will educate attendees on Bitcoin as a tool for escaping financial repression. If you have Burmese friends in Chiang Mai, share this opportunity with them. You can register [here](https://docs.google.com/forms/d/e/1FAIpQLScscuPhxba_Ma040Wwm9-ud7eODWVMpb_8RpFx-12yYbvfl5g/viewform). ## RECOMMENDED CONTENT #### **Bitcoin and Freedom with Alex Gladstein** In a special [episode](https://www.youtube.com/watch?v=hC93o30gUa8) of the “Money Matters” podcast, Jack Mallers, CEO of Strike, speaks with Alex Gladstein, chief strategy officer at HRF, to discuss the powerful link between Bitcoin and financial freedom. Gladstein unpacks how authoritarian regimes manipulate money to control the public and explains why open-source financial tools are critical for resisting oppression. His insights make a compelling case for financial sovereignty as a fundamental human right — and why Bitcoin remains the most effective tool to secure it. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/) @ a012dc82:6458a70d
2025-02-13 04:00:01In the dynamic world of global finance, the interplay between traditional monetary policy and the burgeoning digital asset market is becoming increasingly prominent. The U.S. Federal Reserve's recent pivot towards a more accommodative monetary policy has sparked intense discussion among investors, economists, and cryptocurrency enthusiasts. This shift, characterized by an expected reduction in interest rates, is not just a routine adjustment but a significant move that could have far-reaching implications for various asset classes, including cryptocurrencies like Bitcoin. As we delve into this topic, we aim to unravel the complexities of the Fed's policy change and its potential ripple effects on Bitcoin, a digital asset that has been a subject of much intrigue and speculation. **Table Of Content** - Understanding the Fed's Policy Shift - Impact on Traditional Financial Markets - Bitcoin's Response to Monetary Easing - Analyzing the Economic Backdrop - Bitcoin: A Safe Haven or Risk Asset? - Risks and Opportunities - Conclusion - FAQs **Understanding the Fed's Policy Shift** The Federal Reserve, the guardian of the U.S. monetary system, wields immense influence over global financial markets. Its recent signaling of a dovish turn – an expectation of 75 basis points in rate cuts by 2024 – marks a significant departure from its previous stance. This change is reflective of the Fed's response to a confluence of macroeconomic factors, such as fluctuating inflation rates, global economic uncertainties, and domestic financial stability concerns. The Fed's decisions are closely monitored as they set the tone for economic growth, inflation control, and financial market stability. In this context, the anticipated rate cuts suggest a strategic move to stimulate economic activity by making borrowing cheaper, thereby potentially boosting investment and consumption. However, this policy shift is not without its complexities and nuances, as it must balance the fine line between stimulating growth and controlling inflation. **Impact on Traditional Financial Markets** The ripple effects of the Fed's policy announcement were immediately felt across traditional financial markets. Stock markets, often seen as a barometer of economic sentiment, reacted positively, with indices like the Dow Jones Industrial Average reaching new heights. This surge reflects investors' optimism about the potential for increased corporate profits and economic growth in a lower interest rate environment. Similarly, the bond market experienced a significant rally, with yields on government securities falling as bond prices rose. This movement in the bond market is indicative of investors' expectations of a more accommodative monetary policy, which typically leads to lower yields on fixed-income securities. These market reactions underscore the pivotal role of central bank policies in shaping investor sentiment and the direction of financial markets. They also highlight the interconnectedness of various asset classes, as changes in monetary policy can have cascading effects across different sectors of the economy. **Bitcoin's Response to Monetary Easing** Bitcoin's reaction to the Fed's dovish turn has been a subject of keen interest. The cryptocurrency, which had been experiencing volatility, showed signs of recovery following the Fed's announcement. This response is indicative of Bitcoin's increasing correlation with broader financial market trends, a significant development given its history as an uncorrelated asset. Bitcoin's sensitivity to macroeconomic factors like central bank policies points to its growing integration into the mainstream financial ecosystem. However, this integration also means that Bitcoin is increasingly exposed to the same macroeconomic risks and uncertainties that affect traditional assets. The Fed's policy shift could potentially make Bitcoin more attractive to investors seeking non-traditional assets in a low-interest-rate environment. However, Bitcoin's complex dynamics, including its decentralized nature, limited supply, and regulatory landscape, add layers of complexity to its response to monetary policy changes. **Analyzing the Economic Backdrop** The economic backdrop against which the Fed's policy shift occurs is multifaceted and dynamic. On one hand, the U.S. economy has demonstrated resilience, with robust GDP growth and positive retail sales figures suggesting underlying strength. On the other hand, inflation, though moderated from its peak, remains a concern, hovering above the Fed's target. This economic duality presents a challenging scenario for policymakers, who must navigate the delicate balance between stimulating growth and containing inflation. For investors and market participants, this creates an environment of uncertainty, as they must decipher mixed signals from economic data and policy announcements. In this context, Bitcoin's role and response become even more intriguing, as it operates at the intersection of technology, finance, and macroeconomics. **Bitcoin: A Safe Haven or Risk Asset?** The debate over Bitcoin's classification as a safe haven or a risk asset is intensified by the Fed's easing stance. Traditionally, in a low-interest-rate environment, investors seek assets that can serve as hedges against inflation and currency devaluation. Gold has historically played this role, and Bitcoin, with its fixed supply and digital scarcity, has drawn comparisons to gold. However, Bitcoin's relatively short history and high volatility make it a more complex and potentially riskier asset. The Fed's dovish policy could enhance Bitcoin's appeal as an alternative investment, especially if traditional assets like bonds offer lower returns. However, Bitcoin's classification as a safe haven is still a matter of debate, with opinions divided on its long-term stability and value retention capabilities. **Risks and Opportunities** Investors considering Bitcoin in light of the Fed's policy change face a landscape filled with both risks and opportunities. The potential for a Bitcoin rally in a low-interest-rate environment is counterbalanced by the cryptocurrency's inherent volatility and regulatory uncertainties. Bitcoin's price movements can be dramatic and unpredictable, influenced by a range of factors from technological developments to geopolitical events. Additionally, the regulatory environment for cryptocurrencies is still evolving, with potential changes posing risks to Bitcoin's accessibility and value. Investors must also consider the broader global economic context, including actions by other central banks and international trade dynamics, which can impact Bitcoin's market movement. **Conclusion** The Federal Reserve's shift towards a more accommodative monetary policy in 2024 presents a fascinating scenario for Bitcoin and the broader cryptocurrency market. This development underscores the increasing relevance of digital assets in the global financial landscape and highlights the complex interplay between traditional monetary policies and emerging financial technologies. As Bitcoin continues to evolve and gain acceptance, its response to macroeconomic factors like central bank policies will be a critical area of focus for investors. In navigating this dynamic and uncertain environment, a cautious and well-informed approach is essential for those looking to explore the opportunities and navigate the challenges of cryptocurrency investments. The coming years promise to be a pivotal period in the maturation of Bitcoin as it responds to the shifting tides of global finance. **FAQs** **How does the Federal Reserve's easing stance impact Bitcoin?** The Fed's shift towards lower interest rates can make riskier assets like Bitcoin more attractive to investors. This is because lower rates often lead to reduced yields on traditional investments, prompting investors to seek higher returns elsewhere. **What is the significance of the Fed's 'dot plot' for Bitcoin investors?** The 'dot plot' is a projection of interest rate movements by Federal Reserve members. A shift towards lower rates, as indicated in the recent dot plot, can signal a more accommodative monetary policy, potentially impacting Bitcoin's market as investors adjust their portfolios. **Can Bitcoin be considered a safe haven asset in light of the Fed's policy?** Bitcoin's role as a safe haven asset is debated. While its fixed supply and digital nature offer some safe haven characteristics, its volatility and regulatory uncertainties make it a complex choice compared to traditional safe havens like gold. **What risks should Bitcoin investors consider in the context of the Fed's easing policy?** Investors should be aware of Bitcoin's volatility, regulatory changes, and its sensitivity to macroeconomic factors. Additionally, global economic conditions and actions by other central banks can also influence Bitcoin's market. **How does the economic backdrop influence Bitcoin's response to the Fed's policy?** Economic factors like GDP growth, inflation rates, and retail sales impact investor sentiment and risk appetite, which in turn can affect Bitcoin's market. A strong economy might reduce the appeal of risk assets like Bitcoin, while economic uncertainties can increase their attractiveness. **That's all for today** **If you want more, be sure to follow us on:** **NOSTR: croxroad@getalby.com** **X: @croxroadnews.co** **Instagram: @croxroadnews.co** **Youtube: @croxroadnews** **Store: https://croxroad.store** **Subscribe to CROX ROAD Bitcoin Only Daily Newsletter** **https://www.croxroad.co/subscribe** ***DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.***
@ a012dc82:6458a70d
2025-02-13 04:00:01In the dynamic world of global finance, the interplay between traditional monetary policy and the burgeoning digital asset market is becoming increasingly prominent. The U.S. Federal Reserve's recent pivot towards a more accommodative monetary policy has sparked intense discussion among investors, economists, and cryptocurrency enthusiasts. This shift, characterized by an expected reduction in interest rates, is not just a routine adjustment but a significant move that could have far-reaching implications for various asset classes, including cryptocurrencies like Bitcoin. As we delve into this topic, we aim to unravel the complexities of the Fed's policy change and its potential ripple effects on Bitcoin, a digital asset that has been a subject of much intrigue and speculation. **Table Of Content** - Understanding the Fed's Policy Shift - Impact on Traditional Financial Markets - Bitcoin's Response to Monetary Easing - Analyzing the Economic Backdrop - Bitcoin: A Safe Haven or Risk Asset? - Risks and Opportunities - Conclusion - FAQs **Understanding the Fed's Policy Shift** The Federal Reserve, the guardian of the U.S. monetary system, wields immense influence over global financial markets. Its recent signaling of a dovish turn – an expectation of 75 basis points in rate cuts by 2024 – marks a significant departure from its previous stance. This change is reflective of the Fed's response to a confluence of macroeconomic factors, such as fluctuating inflation rates, global economic uncertainties, and domestic financial stability concerns. The Fed's decisions are closely monitored as they set the tone for economic growth, inflation control, and financial market stability. In this context, the anticipated rate cuts suggest a strategic move to stimulate economic activity by making borrowing cheaper, thereby potentially boosting investment and consumption. However, this policy shift is not without its complexities and nuances, as it must balance the fine line between stimulating growth and controlling inflation. **Impact on Traditional Financial Markets** The ripple effects of the Fed's policy announcement were immediately felt across traditional financial markets. Stock markets, often seen as a barometer of economic sentiment, reacted positively, with indices like the Dow Jones Industrial Average reaching new heights. This surge reflects investors' optimism about the potential for increased corporate profits and economic growth in a lower interest rate environment. Similarly, the bond market experienced a significant rally, with yields on government securities falling as bond prices rose. This movement in the bond market is indicative of investors' expectations of a more accommodative monetary policy, which typically leads to lower yields on fixed-income securities. These market reactions underscore the pivotal role of central bank policies in shaping investor sentiment and the direction of financial markets. They also highlight the interconnectedness of various asset classes, as changes in monetary policy can have cascading effects across different sectors of the economy. **Bitcoin's Response to Monetary Easing** Bitcoin's reaction to the Fed's dovish turn has been a subject of keen interest. The cryptocurrency, which had been experiencing volatility, showed signs of recovery following the Fed's announcement. This response is indicative of Bitcoin's increasing correlation with broader financial market trends, a significant development given its history as an uncorrelated asset. Bitcoin's sensitivity to macroeconomic factors like central bank policies points to its growing integration into the mainstream financial ecosystem. However, this integration also means that Bitcoin is increasingly exposed to the same macroeconomic risks and uncertainties that affect traditional assets. The Fed's policy shift could potentially make Bitcoin more attractive to investors seeking non-traditional assets in a low-interest-rate environment. However, Bitcoin's complex dynamics, including its decentralized nature, limited supply, and regulatory landscape, add layers of complexity to its response to monetary policy changes. **Analyzing the Economic Backdrop** The economic backdrop against which the Fed's policy shift occurs is multifaceted and dynamic. On one hand, the U.S. economy has demonstrated resilience, with robust GDP growth and positive retail sales figures suggesting underlying strength. On the other hand, inflation, though moderated from its peak, remains a concern, hovering above the Fed's target. This economic duality presents a challenging scenario for policymakers, who must navigate the delicate balance between stimulating growth and containing inflation. For investors and market participants, this creates an environment of uncertainty, as they must decipher mixed signals from economic data and policy announcements. In this context, Bitcoin's role and response become even more intriguing, as it operates at the intersection of technology, finance, and macroeconomics. **Bitcoin: A Safe Haven or Risk Asset?** The debate over Bitcoin's classification as a safe haven or a risk asset is intensified by the Fed's easing stance. Traditionally, in a low-interest-rate environment, investors seek assets that can serve as hedges against inflation and currency devaluation. Gold has historically played this role, and Bitcoin, with its fixed supply and digital scarcity, has drawn comparisons to gold. However, Bitcoin's relatively short history and high volatility make it a more complex and potentially riskier asset. The Fed's dovish policy could enhance Bitcoin's appeal as an alternative investment, especially if traditional assets like bonds offer lower returns. However, Bitcoin's classification as a safe haven is still a matter of debate, with opinions divided on its long-term stability and value retention capabilities. **Risks and Opportunities** Investors considering Bitcoin in light of the Fed's policy change face a landscape filled with both risks and opportunities. The potential for a Bitcoin rally in a low-interest-rate environment is counterbalanced by the cryptocurrency's inherent volatility and regulatory uncertainties. Bitcoin's price movements can be dramatic and unpredictable, influenced by a range of factors from technological developments to geopolitical events. Additionally, the regulatory environment for cryptocurrencies is still evolving, with potential changes posing risks to Bitcoin's accessibility and value. Investors must also consider the broader global economic context, including actions by other central banks and international trade dynamics, which can impact Bitcoin's market movement. **Conclusion** The Federal Reserve's shift towards a more accommodative monetary policy in 2024 presents a fascinating scenario for Bitcoin and the broader cryptocurrency market. This development underscores the increasing relevance of digital assets in the global financial landscape and highlights the complex interplay between traditional monetary policies and emerging financial technologies. As Bitcoin continues to evolve and gain acceptance, its response to macroeconomic factors like central bank policies will be a critical area of focus for investors. In navigating this dynamic and uncertain environment, a cautious and well-informed approach is essential for those looking to explore the opportunities and navigate the challenges of cryptocurrency investments. The coming years promise to be a pivotal period in the maturation of Bitcoin as it responds to the shifting tides of global finance. **FAQs** **How does the Federal Reserve's easing stance impact Bitcoin?** The Fed's shift towards lower interest rates can make riskier assets like Bitcoin more attractive to investors. This is because lower rates often lead to reduced yields on traditional investments, prompting investors to seek higher returns elsewhere. **What is the significance of the Fed's 'dot plot' for Bitcoin investors?** The 'dot plot' is a projection of interest rate movements by Federal Reserve members. A shift towards lower rates, as indicated in the recent dot plot, can signal a more accommodative monetary policy, potentially impacting Bitcoin's market as investors adjust their portfolios. **Can Bitcoin be considered a safe haven asset in light of the Fed's policy?** Bitcoin's role as a safe haven asset is debated. While its fixed supply and digital nature offer some safe haven characteristics, its volatility and regulatory uncertainties make it a complex choice compared to traditional safe havens like gold. **What risks should Bitcoin investors consider in the context of the Fed's easing policy?** Investors should be aware of Bitcoin's volatility, regulatory changes, and its sensitivity to macroeconomic factors. Additionally, global economic conditions and actions by other central banks can also influence Bitcoin's market. **How does the economic backdrop influence Bitcoin's response to the Fed's policy?** Economic factors like GDP growth, inflation rates, and retail sales impact investor sentiment and risk appetite, which in turn can affect Bitcoin's market. A strong economy might reduce the appeal of risk assets like Bitcoin, while economic uncertainties can increase their attractiveness. **That's all for today** **If you want more, be sure to follow us on:** **NOSTR: croxroad@getalby.com** **X: @croxroadnews.co** **Instagram: @croxroadnews.co** **Youtube: @croxroadnews** **Store: https://croxroad.store** **Subscribe to CROX ROAD Bitcoin Only Daily Newsletter** **https://www.croxroad.co/subscribe** ***DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.*** @ 57d1a264:69f1fee1
2025-02-13 03:45:23 **What You Will Learn:** - Understanding the concept of cybersecurity - Networking Basics - Operating Systems Overview - Introduction to Kali Linux - Threat Actors and Cyber Threats - Ethical Hacking Techniques and Tools. **How to Register:** Use this link to Register. https://forms.gle/L8AGLCWU4djwUXxz9 originally posted at https://stacker.news/items/884407
@ 57d1a264:69f1fee1
2025-02-13 03:45:23 **What You Will Learn:** - Understanding the concept of cybersecurity - Networking Basics - Operating Systems Overview - Introduction to Kali Linux - Threat Actors and Cyber Threats - Ethical Hacking Techniques and Tools. **How to Register:** Use this link to Register. https://forms.gle/L8AGLCWU4djwUXxz9 originally posted at https://stacker.news/items/884407 @ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York. DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million. The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture. Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry. ![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
@ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York. DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million. The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture. Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry. ![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg) @ f6488c62:c929299d
2025-02-13 02:39:41Lowering interest rates is one of the tools that central banks use to manage the economy, especially during periods of inflation, which causes the prices of goods and services to rise. Lowering interest rates not only helps stimulate spending but can also foster sustainable growth in businesses and labor markets. Access to Capital and Economic Stimulation When interest rates are lowered, the public can access capital more easily. With lower interest rates, borrowing becomes less burdensome, giving individuals and businesses the opportunity to start new ventures or expand existing businesses. This leads to increased investment and spending, which in turn keeps the economy circulating and growing. For instance, when people can easily borrow money to start a new business—such as an online store or a product manufacturing business—the increase in entrepreneurs and the availability of goods in the market will ensure that the supply is sufficient to meet consumer demand. This, in turn, prevents prices from rising too much due to a lack of supply. Reducing Inflation by Increasing Supply Increasing the supply of goods and services in the market can significantly help in controlling inflation. When there are more goods or services available to meet market demand, competition among producers will naturally drive prices down. This is the basic principle of market dynamics: when there’s enough supply, prices are less likely to increase, even in times of high demand. In addition, increasing supply helps address shortages, which are one of the key drivers of rising prices. When there is enough product available to satisfy demand, inflationary pressures can be relieved, and prices can stabilize. Redistributing Income and Reducing Inequality Lower interest rates also play a crucial role in redistributing income within society. By making access to capital easier, especially for those with lower or middle incomes, the public’s purchasing power increases, which can stimulate spending on essential goods and services. When people have more money in hand, they are better able to access necessary products. This boosts demand in the market. However, alongside this increased demand, sufficient supply is needed to prevent prices from rising uncontrollably, which can lead to inflation. Moreover, supporting the population through welfare programs or initiatives that allow everyone to access education and investment opportunities helps individuals create products and value in the market. A diverse market with a variety of products increases production efficiency and helps mitigate economic inequality, ensuring a more balanced and inclusive economy. Conclusion Lowering interest rates and redistributing income effectively can stimulate economic growth and reduce inflation. This works by ensuring there is sufficient supply to meet market demand, while also providing capital that allows the public to start new businesses and generate new products in the market. For sustainable long-term economic growth, managing inflation should go hand in hand with investing in infrastructure and ensuring wealth distribution. This ensures that everyone has equal access to opportunities, leading to steady economic growth without negatively impacting the majority of society. In summary, lowering interest rates is a key tool in stimulating the economy and reducing inflation, especially when the economy faces imbalances. It not only increases supply, but also promotes income redistribution and the creation of an economy that is more equitable in the long run.
@ f6488c62:c929299d
2025-02-13 02:39:41Lowering interest rates is one of the tools that central banks use to manage the economy, especially during periods of inflation, which causes the prices of goods and services to rise. Lowering interest rates not only helps stimulate spending but can also foster sustainable growth in businesses and labor markets. Access to Capital and Economic Stimulation When interest rates are lowered, the public can access capital more easily. With lower interest rates, borrowing becomes less burdensome, giving individuals and businesses the opportunity to start new ventures or expand existing businesses. This leads to increased investment and spending, which in turn keeps the economy circulating and growing. For instance, when people can easily borrow money to start a new business—such as an online store or a product manufacturing business—the increase in entrepreneurs and the availability of goods in the market will ensure that the supply is sufficient to meet consumer demand. This, in turn, prevents prices from rising too much due to a lack of supply. Reducing Inflation by Increasing Supply Increasing the supply of goods and services in the market can significantly help in controlling inflation. When there are more goods or services available to meet market demand, competition among producers will naturally drive prices down. This is the basic principle of market dynamics: when there’s enough supply, prices are less likely to increase, even in times of high demand. In addition, increasing supply helps address shortages, which are one of the key drivers of rising prices. When there is enough product available to satisfy demand, inflationary pressures can be relieved, and prices can stabilize. Redistributing Income and Reducing Inequality Lower interest rates also play a crucial role in redistributing income within society. By making access to capital easier, especially for those with lower or middle incomes, the public’s purchasing power increases, which can stimulate spending on essential goods and services. When people have more money in hand, they are better able to access necessary products. This boosts demand in the market. However, alongside this increased demand, sufficient supply is needed to prevent prices from rising uncontrollably, which can lead to inflation. Moreover, supporting the population through welfare programs or initiatives that allow everyone to access education and investment opportunities helps individuals create products and value in the market. A diverse market with a variety of products increases production efficiency and helps mitigate economic inequality, ensuring a more balanced and inclusive economy. Conclusion Lowering interest rates and redistributing income effectively can stimulate economic growth and reduce inflation. This works by ensuring there is sufficient supply to meet market demand, while also providing capital that allows the public to start new businesses and generate new products in the market. For sustainable long-term economic growth, managing inflation should go hand in hand with investing in infrastructure and ensuring wealth distribution. This ensures that everyone has equal access to opportunities, leading to steady economic growth without negatively impacting the majority of society. In summary, lowering interest rates is a key tool in stimulating the economy and reducing inflation, especially when the economy faces imbalances. It not only increases supply, but also promotes income redistribution and the creation of an economy that is more equitable in the long run. @ 3b7fc823:e194354f
2025-02-13 02:25:42site:example.com intitle:"index of" inurl:admin intext:"password" site:example.com site:.gov site:.edu site:*.mil inurl:login inurl:admin inurl:dashboard inurl:portal intitle:"admin login" intitle:"index of /" intitle:"index of" "parent directory" intitle:"index of" "backup" filetype:pdf "confidential" filetype:xls "username | password" filetype:doc "top secret" filetype:sql "database" intext:"username" intext:"password" intext:"login" intext:"password" filetype:txt "passwords" inurl:"viewerframe?mode=" inurl:"/view.shtml" inurl:"/view/index.shtml" intitle:"index of" "wp-config.php" inurl:".git" filetype:xls intext:"email" filetype:csv intext:"email" inurl:"/setup.cgi?next_file=netgear.cfg" inurl:"/wificonf.html"
@ 3b7fc823:e194354f
2025-02-13 02:25:42site:example.com intitle:"index of" inurl:admin intext:"password" site:example.com site:.gov site:.edu site:*.mil inurl:login inurl:admin inurl:dashboard inurl:portal intitle:"admin login" intitle:"index of /" intitle:"index of" "parent directory" intitle:"index of" "backup" filetype:pdf "confidential" filetype:xls "username | password" filetype:doc "top secret" filetype:sql "database" intext:"username" intext:"password" intext:"login" intext:"password" filetype:txt "passwords" inurl:"viewerframe?mode=" inurl:"/view.shtml" inurl:"/view/index.shtml" intitle:"index of" "wp-config.php" inurl:".git" filetype:xls intext:"email" filetype:csv intext:"email" inurl:"/setup.cgi?next_file=netgear.cfg" inurl:"/wificonf.html" @ fd78c37f:a0ec0833
2025-02-13 02:24:48In this edition, we invited Rafael from Bitcoin É Aqui to share the development of his community and its efforts in promoting Bitcoin adoption. From establishing a Bitcoin-friendly environment in Rolante to organizing and supporting events like the Bitcoin Spring Festival and KuchenFest, Rafael highlighted Bitcoin's impact on the local economy and tourism industry. **YakiHonne**: Today, we are honored to invite Rafael from Bitcoin é Aqui to join us. Before we dive in, I'd like to take a moment to introduce YakiHonne and share a bit about what we do. YakiHonne is a decentralized media client built on the Nostr protocol that enables freedom of speech through technology. It empowers creators to create their own voice, assets, and features. It also allows features like smart widgets, verified notes, and focuses on long-form articles. Now today we'll be exploring more about the Bitcoin community. Rafael, could you please briefly introduce what sparked your interest in Bitcoin, and what motivated you to create this community? **Rafael**:Like many, Stim's and his wife Camila's initial interest was in technology— a completely new way to transfer money with full self-custody. From the beginning, the project focused on the payment network, and at the time, they didn’t realize it would evolve into “A Project.” **YakiHonne**: Could you share how your community got started, the strategies you used to attract members, and the early challenges you encountered? **Rafael**:From the start, we were all about building a payment network. We began by paying our barber, gardener, and other service providers with Bitcoin. After a few close friends joined, word started to spread—even though some were worried about scams and Bitcoin's legality. To address these concerns, we held a talk at the City's Trade Association on how merchants could legally accept Bitcoin. We expected 5 to 10 friends, but over 60 merchants attended! Today, we’re proud to say that our city is the most Bitcoin-friendly in the world, with more than 40% of stores accepting it. From plumbers to supermarkets, it’s amazing to see our community featured on the BitcoinMap website.  **YakiHonne**: What principles guide the community, and how do you maintain trust and reliability in discussions? **Rafael**:Like Bitcoin itself, decentralization is our core principle. The project "Bitcoin É Aqui" (loosely translated as "Bitcoin is Here") assists merchants in setting up Lightning wallets and offers best practices. However, every merchant is free to operate as they see fit—choosing whether to follow our advice or to use any wallet they prefer. Moreover, many experienced merchants help onboard newcomers, building trust through established networks and reinforcing our decentralized approach. **YakiHonne**: How do you educate members and keep them updated on Bitcoin developments? **Rafael**:We have a group chat where we post some news, but in Brazil, almost everyone already uses WhatsApp for communication, and news usually spreads through these groups, again highlighting the decentralized nature of the Project. **YakiHonne**: What initiatives has the community undertaken to promote Bitcoin adoption, and what results have you seen? **Rafael**:Of course, the rising coin value draws attention, but the main attraction is tourists coming to Rolante to learn about the project. Rolante was already famed for its natural wonders—majestic mountains and breathtaking waterfalls. Combined with Bitcoin’s innovative acceptance as a payment method, it has become an even stronger magnet for visitors. **Rafael**:In Rolante, living completely on Bitcoin is a reality. Here, you'll find travel agencies, professional tour guides, and a variety of services—from department stores and opticians to real estate agents, construction companies, architects, furniture stores, building materials suppliers, and solar energy providers. In the healthcare sector, you can rely on pharmacies, massage therapists, physiotherapists, and advanced dental services; even the city hospital accepts Bitcoin as payment.  **YakiHonne**: What are the community’s goals for the next 6-12 months, and how do you see it evolving with Bitcoin’s growth? **Rafael**:As a project, Bitcoin É Aqui doesn’t dictate what the community should do, but we support many events like Pizza Day, Bitcoin Spring Festival, Bier Rock, KuchenFest. One major event is the biennial Bitcoin Spring Festival (BSF). The Bitcoin Spring Festival (BSF) is a key event in the Rolante Bitcoin community, aimed at promoting Bitcoin adoption and circular economy development. This year, the festival focuses on "Bitcoinization," bringing together notable figures in the Bitcoin space to showcase a real Bitcoin economic ecosystem. During the event, all transactions will be conducted via the Lightning Network, with Coinos.io and Wallet Of Satoshi recommended. BSF is not just a celebration but a movement toward financial freedom.  **Rafael**:This March, Rolante will host its most traditional event, KuchenFest, celebrating the local traditional bread delicacy. The event centers around the sweet bread Cuca, bringing together candy makers and Cuca enthusiasts to share recipes, techniques, and stories. Additionally, the festival features live music, folk dances, and family activities, showcasing rich cultural traditions. We will help the event accept and promote the use of Bitcoin.
@ fd78c37f:a0ec0833
2025-02-13 02:24:48In this edition, we invited Rafael from Bitcoin É Aqui to share the development of his community and its efforts in promoting Bitcoin adoption. From establishing a Bitcoin-friendly environment in Rolante to organizing and supporting events like the Bitcoin Spring Festival and KuchenFest, Rafael highlighted Bitcoin's impact on the local economy and tourism industry. **YakiHonne**: Today, we are honored to invite Rafael from Bitcoin é Aqui to join us. Before we dive in, I'd like to take a moment to introduce YakiHonne and share a bit about what we do. YakiHonne is a decentralized media client built on the Nostr protocol that enables freedom of speech through technology. It empowers creators to create their own voice, assets, and features. It also allows features like smart widgets, verified notes, and focuses on long-form articles. Now today we'll be exploring more about the Bitcoin community. Rafael, could you please briefly introduce what sparked your interest in Bitcoin, and what motivated you to create this community? **Rafael**:Like many, Stim's and his wife Camila's initial interest was in technology— a completely new way to transfer money with full self-custody. From the beginning, the project focused on the payment network, and at the time, they didn’t realize it would evolve into “A Project.” **YakiHonne**: Could you share how your community got started, the strategies you used to attract members, and the early challenges you encountered? **Rafael**:From the start, we were all about building a payment network. We began by paying our barber, gardener, and other service providers with Bitcoin. After a few close friends joined, word started to spread—even though some were worried about scams and Bitcoin's legality. To address these concerns, we held a talk at the City's Trade Association on how merchants could legally accept Bitcoin. We expected 5 to 10 friends, but over 60 merchants attended! Today, we’re proud to say that our city is the most Bitcoin-friendly in the world, with more than 40% of stores accepting it. From plumbers to supermarkets, it’s amazing to see our community featured on the BitcoinMap website.  **YakiHonne**: What principles guide the community, and how do you maintain trust and reliability in discussions? **Rafael**:Like Bitcoin itself, decentralization is our core principle. The project "Bitcoin É Aqui" (loosely translated as "Bitcoin is Here") assists merchants in setting up Lightning wallets and offers best practices. However, every merchant is free to operate as they see fit—choosing whether to follow our advice or to use any wallet they prefer. Moreover, many experienced merchants help onboard newcomers, building trust through established networks and reinforcing our decentralized approach. **YakiHonne**: How do you educate members and keep them updated on Bitcoin developments? **Rafael**:We have a group chat where we post some news, but in Brazil, almost everyone already uses WhatsApp for communication, and news usually spreads through these groups, again highlighting the decentralized nature of the Project. **YakiHonne**: What initiatives has the community undertaken to promote Bitcoin adoption, and what results have you seen? **Rafael**:Of course, the rising coin value draws attention, but the main attraction is tourists coming to Rolante to learn about the project. Rolante was already famed for its natural wonders—majestic mountains and breathtaking waterfalls. Combined with Bitcoin’s innovative acceptance as a payment method, it has become an even stronger magnet for visitors. **Rafael**:In Rolante, living completely on Bitcoin is a reality. Here, you'll find travel agencies, professional tour guides, and a variety of services—from department stores and opticians to real estate agents, construction companies, architects, furniture stores, building materials suppliers, and solar energy providers. In the healthcare sector, you can rely on pharmacies, massage therapists, physiotherapists, and advanced dental services; even the city hospital accepts Bitcoin as payment.  **YakiHonne**: What are the community’s goals for the next 6-12 months, and how do you see it evolving with Bitcoin’s growth? **Rafael**:As a project, Bitcoin É Aqui doesn’t dictate what the community should do, but we support many events like Pizza Day, Bitcoin Spring Festival, Bier Rock, KuchenFest. One major event is the biennial Bitcoin Spring Festival (BSF). The Bitcoin Spring Festival (BSF) is a key event in the Rolante Bitcoin community, aimed at promoting Bitcoin adoption and circular economy development. This year, the festival focuses on "Bitcoinization," bringing together notable figures in the Bitcoin space to showcase a real Bitcoin economic ecosystem. During the event, all transactions will be conducted via the Lightning Network, with Coinos.io and Wallet Of Satoshi recommended. BSF is not just a celebration but a movement toward financial freedom.  **Rafael**:This March, Rolante will host its most traditional event, KuchenFest, celebrating the local traditional bread delicacy. The event centers around the sweet bread Cuca, bringing together candy makers and Cuca enthusiasts to share recipes, techniques, and stories. Additionally, the festival features live music, folk dances, and family activities, showcasing rich cultural traditions. We will help the event accept and promote the use of Bitcoin. @ fd208ee8:0fd927c1
2025-01-23 15:31:24## Planning Alexandria People keep asking what features nostr:npub1s3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqd975wz has planned for #Alexandria, but they're not set in stone because we're an agile project. What we do have, is lots of tickets on our Kanban boards and a naming scheme, where we use a famous person's last name, to signify the release goals.  ### Gutenberg v 0.1.0 (after the inventor of the printing press) will contain the features needed to read and write [NIP-62 Curated Publications](https://github.com/nostr-protocol/nips/pull/1600), as well as encompassing the complex infrastructure, architecture, documentation, and personnel we require to make this all run smoothly and look easy.  ### Euler v 0.2.0 (after a mathematician credited with establishing graph theory) will contain the features for deep-searching, visually exploring, and smartly navigating the data set, wiki page display, annotating and citing the publications, exporting to other formats (like PDF, ePUB, and LaTeX), and commenting/reviewing. To help with the heavy lifting, we will be swapping out the core with our own Nostr SDK called "Aedile".  ### Defoe v 0.3.0 (after an author who perfected the novel format) will be all about our favorite writers. We will be focusing upon profile data, payment systems, book clubs and communities, and stylesheets. That is everything we have planned, for the v1.0 edition, and we consider that version to be a true product. As for after that, a teaser... 
@ fd208ee8:0fd927c1
2025-01-23 15:31:24## Planning Alexandria People keep asking what features nostr:npub1s3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqd975wz has planned for #Alexandria, but they're not set in stone because we're an agile project. What we do have, is lots of tickets on our Kanban boards and a naming scheme, where we use a famous person's last name, to signify the release goals.  ### Gutenberg v 0.1.0 (after the inventor of the printing press) will contain the features needed to read and write [NIP-62 Curated Publications](https://github.com/nostr-protocol/nips/pull/1600), as well as encompassing the complex infrastructure, architecture, documentation, and personnel we require to make this all run smoothly and look easy.  ### Euler v 0.2.0 (after a mathematician credited with establishing graph theory) will contain the features for deep-searching, visually exploring, and smartly navigating the data set, wiki page display, annotating and citing the publications, exporting to other formats (like PDF, ePUB, and LaTeX), and commenting/reviewing. To help with the heavy lifting, we will be swapping out the core with our own Nostr SDK called "Aedile".  ### Defoe v 0.3.0 (after an author who perfected the novel format) will be all about our favorite writers. We will be focusing upon profile data, payment systems, book clubs and communities, and stylesheets. That is everything we have planned, for the v1.0 edition, and we consider that version to be a true product. As for after that, a teaser...  @ 4506e04e:8c16ba04
2025-01-22 16:37:08If you are a researcher in the field of medicine, you are most likely very familiar with PubMed – where you get citations for the articles and studies that drive your work forward. PubMed Central (PMC), the full-text repository of life sciences journal literature managed by the National Library of Medicine (NLM), was established in 2000. Its creation marked a significant milestone in providing open access to biomedical research. Since 2005, PMC has served as the designated repository for papers submitted under the NIH Public Access Policy, reflecting the growing emphasis on transparency and accessibility in scientific research. Over the years, PMC has expanded its scope, becoming a repository for papers aligned with public and open access policies from various research funding organizations, both within and beyond biomedical sciences. ## Funding and Partnerships NLM’s operations, including PubMed and PMC, are supported by a combination of government funding and contributions from influential entities such as The Bill & Melinda Gates Foundation. The Bill and Melinda Gates Foundation receives significant donations from pharmaceutical companies, as well as other organizations and individuals. The exact amount of money donated by each company can vary from year to year, but here are some examples of the amounts donated by the pharmaceutical companies: **GSK (GlaxoSmithKline):** - In 2020, GSK donated $100 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, GSK donated $50 million to the Gates Foundation to support the development of a new malaria vaccine. **Pfizer:** - In 2020, Pfizer donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, Pfizer donated $25 million to the Gates Foundation to support the development of a new malaria vaccine. **Merck & Co.:** - In 2020, Merck donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, Merck donated $25 million to the Gates Foundation to support the development of a new malaria vaccine. **Novartis:** - In 2020, Novartis donated $20 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis. - In 2019, Novartis donated $10 million to the Gates Foundation to support the development of a new malaria vaccine. **Johnson & Johnson:** - In 2020, Johnson & Johnson donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, Johnson & Johnson donated $25 million to the Gates Foundation to support the development of a new malaria vaccine. **Sanofi:** - In 2020, Sanofi donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis. - In 2019, Sanofi donated $10 million to the Gates Foundation to support the development of a new malaria vaccine. **AstraZeneca:** - In 2020, AstraZeneca donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis. - In 2019, AstraZeneca donated $10 million to the Gates Foundation to support the development of a new malaria vaccine. **Eli Lilly and Company:** - In 2020, Eli Lilly donated $10 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis. - In 2019, Eli Lilly donated $5 million to the Gates Foundation to support the development of a new malaria vaccine. Additionally, NLM website [https://cdn.ncbi.nlm.nih.gov/pmc/cms/files/PMCFunderDepositList.xlsx] (list over 200)(!) organisations that are founding it. What could go wrong one might ask?! ## The Centralization Challenge While PubMed and PMC have played a pivotal role in democratizing access to scientific literature, their centralized nature presents vulnerabilities. Over the past century healthcare has grown to become one of the most profitable industries and to believe that the healthcare system we have today is the best we can do is far from understatement. PubMed's reliance on centralized funding and decision-making processes makes it susceptible to external influences, including lobbying by powerful entities. Moreover, the centralized infrastructure allows for content to be published and removed with relative ease, often without leaving a trace. This raises concerns about the integrity and permanence of the scientific record, particularly in contentious or politically sensitive areas of research. The ability to alter or erase information from PubMed undermines trust in the system’s objectivity and neutrality. Researchers and the public alike depend on these repositories for reliable and impartial access to scientific knowledge. Any perceived or actual manipulation of content can erode confidence in the platform and compromise its foundational mission. ## The Case for Decentralization To address these challenges, a decentralized alternative built on emerging technologies, such as the Nostr protocol, could offer significant advantages. A decentralized platform would: - **Enhance Resilience:** By distributing data across a network of relays, a decentralized system would eliminate single points of failure, ensuring the scientific record remains intact and always accessible even in the face of technical or political disruptions. - **Increase Transparency:** Decentralized systems inherently log changes, making it nearly impossible to alter or remove content without leaving an auditable trail. This transparency would bolster trust in the integrity of the research. - **Reduce Susceptibility to Lobbying:** Without centralized control, the influence of external entities on the platform’s content would be significantly diminished, preserving the objectivity of the scientific record. - **Foster Open Collaboration:** A decentralized approach aligns with the principles of open science, encouraging global collaboration without the constraints of centralized oversight or bias introduced by big pharma lobby. ## Conclusion While PubMed and PMC have been instrumental in advancing access to scientific literature, their centralized nature leaves them vulnerable to manipulation and external pressures. A shift toward a decentralized, censorship-resistant platform would address these vulnerabilities and provide a more robust and trustless repository for scientific knowledge. Groundbreaking research that dares to challenge the pharmaceutical industry's status quo could be published anonymously, following in the footsteps of the Bitcoin whitepaper's pseudonymous author, Satoshi Nakamoto. Leveraging technologies like the Nostr protocol, the research community can build a system that ensures the permanence, integrity, and impartiality of the scientific record for generations to come.
@ 4506e04e:8c16ba04
2025-01-22 16:37:08If you are a researcher in the field of medicine, you are most likely very familiar with PubMed – where you get citations for the articles and studies that drive your work forward. PubMed Central (PMC), the full-text repository of life sciences journal literature managed by the National Library of Medicine (NLM), was established in 2000. Its creation marked a significant milestone in providing open access to biomedical research. Since 2005, PMC has served as the designated repository for papers submitted under the NIH Public Access Policy, reflecting the growing emphasis on transparency and accessibility in scientific research. Over the years, PMC has expanded its scope, becoming a repository for papers aligned with public and open access policies from various research funding organizations, both within and beyond biomedical sciences. ## Funding and Partnerships NLM’s operations, including PubMed and PMC, are supported by a combination of government funding and contributions from influential entities such as The Bill & Melinda Gates Foundation. The Bill and Melinda Gates Foundation receives significant donations from pharmaceutical companies, as well as other organizations and individuals. The exact amount of money donated by each company can vary from year to year, but here are some examples of the amounts donated by the pharmaceutical companies: **GSK (GlaxoSmithKline):** - In 2020, GSK donated $100 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, GSK donated $50 million to the Gates Foundation to support the development of a new malaria vaccine. **Pfizer:** - In 2020, Pfizer donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, Pfizer donated $25 million to the Gates Foundation to support the development of a new malaria vaccine. **Merck & Co.:** - In 2020, Merck donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, Merck donated $25 million to the Gates Foundation to support the development of a new malaria vaccine. **Novartis:** - In 2020, Novartis donated $20 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis. - In 2019, Novartis donated $10 million to the Gates Foundation to support the development of a new malaria vaccine. **Johnson & Johnson:** - In 2020, Johnson & Johnson donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS. - In 2019, Johnson & Johnson donated $25 million to the Gates Foundation to support the development of a new malaria vaccine. **Sanofi:** - In 2020, Sanofi donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis. - In 2019, Sanofi donated $10 million to the Gates Foundation to support the development of a new malaria vaccine. **AstraZeneca:** - In 2020, AstraZeneca donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis. - In 2019, AstraZeneca donated $10 million to the Gates Foundation to support the development of a new malaria vaccine. **Eli Lilly and Company:** - In 2020, Eli Lilly donated $10 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis. - In 2019, Eli Lilly donated $5 million to the Gates Foundation to support the development of a new malaria vaccine. Additionally, NLM website [https://cdn.ncbi.nlm.nih.gov/pmc/cms/files/PMCFunderDepositList.xlsx] (list over 200)(!) organisations that are founding it. What could go wrong one might ask?! ## The Centralization Challenge While PubMed and PMC have played a pivotal role in democratizing access to scientific literature, their centralized nature presents vulnerabilities. Over the past century healthcare has grown to become one of the most profitable industries and to believe that the healthcare system we have today is the best we can do is far from understatement. PubMed's reliance on centralized funding and decision-making processes makes it susceptible to external influences, including lobbying by powerful entities. Moreover, the centralized infrastructure allows for content to be published and removed with relative ease, often without leaving a trace. This raises concerns about the integrity and permanence of the scientific record, particularly in contentious or politically sensitive areas of research. The ability to alter or erase information from PubMed undermines trust in the system’s objectivity and neutrality. Researchers and the public alike depend on these repositories for reliable and impartial access to scientific knowledge. Any perceived or actual manipulation of content can erode confidence in the platform and compromise its foundational mission. ## The Case for Decentralization To address these challenges, a decentralized alternative built on emerging technologies, such as the Nostr protocol, could offer significant advantages. A decentralized platform would: - **Enhance Resilience:** By distributing data across a network of relays, a decentralized system would eliminate single points of failure, ensuring the scientific record remains intact and always accessible even in the face of technical or political disruptions. - **Increase Transparency:** Decentralized systems inherently log changes, making it nearly impossible to alter or remove content without leaving an auditable trail. This transparency would bolster trust in the integrity of the research. - **Reduce Susceptibility to Lobbying:** Without centralized control, the influence of external entities on the platform’s content would be significantly diminished, preserving the objectivity of the scientific record. - **Foster Open Collaboration:** A decentralized approach aligns with the principles of open science, encouraging global collaboration without the constraints of centralized oversight or bias introduced by big pharma lobby. ## Conclusion While PubMed and PMC have been instrumental in advancing access to scientific literature, their centralized nature leaves them vulnerable to manipulation and external pressures. A shift toward a decentralized, censorship-resistant platform would address these vulnerabilities and provide a more robust and trustless repository for scientific knowledge. Groundbreaking research that dares to challenge the pharmaceutical industry's status quo could be published anonymously, following in the footsteps of the Bitcoin whitepaper's pseudonymous author, Satoshi Nakamoto. Leveraging technologies like the Nostr protocol, the research community can build a system that ensures the permanence, integrity, and impartiality of the scientific record for generations to come. @ ac6f9572:8a6853dd
2025-02-13 02:05:22I attended Sats ‘n’ Facts to share my art, joining other Nostr artists in exhibiting our work at the event’s very first venue. It was a great opportunity to connect with fellow creatives, including Siritravelsketch, whose work I’ve admired on Nostr for some time. Meeting other artists in real life is always inspiring—there’s an undeniable creative bond that comes from sharing our passion in person.  Sats ‘n’ Facts is an Unconference, meaning there’s no strict schedule—everything is open for participants. It’s all about the connections made, the synergy shared, and, for the developers attending, the excitement of a hackathon. (A hackathon is an event where people collaborate intensively on engineering projects, often within 24 to 48 hours.)  My goal as an artist is to become a bridge between the Bitcoin tech world and the Bitcoin art and design space. Bitcoin empowers us by providing greater (financial) freedom, and with that freedom comes more time to pursue what we truly love—so in a way, you never have to “work” again. 😊  Nostr is a great example of how bubbles 🫧 POP, leading to new collaborations. Without tech, artists wouldn’t have a way to share their work, and without artists, creatives, and plebs, developers would have no one to build for. Both sides are essential for organic growth. This kind of synergy can only thrive in a decentralized system—otherwise, it risks being captured by big corporations. And that single point of failure is one of the biggest challenges we face in the world today.  Decentralization is freedom. Events like Sats ‘n’ Facts give us the opportunity to collaborate, create, and contribute to a more decentralized world—one where more people can truly become free.  Can’t wait to join the next Sats’n’facts. Maybe Barcelona!? * * * Originally article published by @BitPopArt on @YakiHonne: https://yakihonne.com/article/naddr1qvzqqqr4gupzqsa64uxz3ek0kx2mzlhqs0seavay4l06c4xek6a0zup8pmge8c6vqq242en0tukk7u2fwe8kkjrpv3ykgjtzwfsk5hmmfyp #art #nostr #ThaiNostrich #artonnostr #artstr originally posted at https://stacker.news/items/884327
@ ac6f9572:8a6853dd
2025-02-13 02:05:22I attended Sats ‘n’ Facts to share my art, joining other Nostr artists in exhibiting our work at the event’s very first venue. It was a great opportunity to connect with fellow creatives, including Siritravelsketch, whose work I’ve admired on Nostr for some time. Meeting other artists in real life is always inspiring—there’s an undeniable creative bond that comes from sharing our passion in person.  Sats ‘n’ Facts is an Unconference, meaning there’s no strict schedule—everything is open for participants. It’s all about the connections made, the synergy shared, and, for the developers attending, the excitement of a hackathon. (A hackathon is an event where people collaborate intensively on engineering projects, often within 24 to 48 hours.)  My goal as an artist is to become a bridge between the Bitcoin tech world and the Bitcoin art and design space. Bitcoin empowers us by providing greater (financial) freedom, and with that freedom comes more time to pursue what we truly love—so in a way, you never have to “work” again. 😊  Nostr is a great example of how bubbles 🫧 POP, leading to new collaborations. Without tech, artists wouldn’t have a way to share their work, and without artists, creatives, and plebs, developers would have no one to build for. Both sides are essential for organic growth. This kind of synergy can only thrive in a decentralized system—otherwise, it risks being captured by big corporations. And that single point of failure is one of the biggest challenges we face in the world today.  Decentralization is freedom. Events like Sats ‘n’ Facts give us the opportunity to collaborate, create, and contribute to a more decentralized world—one where more people can truly become free.  Can’t wait to join the next Sats’n’facts. Maybe Barcelona!? * * * Originally article published by @BitPopArt on @YakiHonne: https://yakihonne.com/article/naddr1qvzqqqr4gupzqsa64uxz3ek0kx2mzlhqs0seavay4l06c4xek6a0zup8pmge8c6vqq242en0tukk7u2fwe8kkjrpv3ykgjtzwfsk5hmmfyp #art #nostr #ThaiNostrich #artonnostr #artstr originally posted at https://stacker.news/items/884327 @ df478568:2a951e67
2025-02-13 02:04:30In the very early days, Nostr was pretty much troll-free. It was one of my favorite things about it, but I suspected this was only the case because only hardcore bitcoiners were on there. Now that the network is growing, there is more diversity of ideas. Ideology tends to make people mean. Mean people suck, so I try to remain respectful even when I disagree with others. I am not a fan of communism, but enjoy reading other perspectives. I do not wish to censor any speech at all, especially speech I do not agree with. The freedom of speech is not about the First Amendment to me. It's about creating a space that is safe for free speech. Platforms are not a safe space for free speech. The safety of free speech is in peril on platforms. Nostr is a space where people can speak freely in an open Internet-connected society. There is some speech I would rather not see. I wish some people did not say certain things, but I do not want to stop them. If we censor the worst speech, the speech does not go away. It merely goes underground and creates bad speech silos where people hide their true selves and go only speak to people just like them. Censorship is like prison for ideas. Prisoners improve their robbery skills because they exchange ideas with other criminals. It's like a conference for criminals. Fascists get more fascist when they only have permission to talk to fellow fascists. Communists get more communist when they can only talk to other communists. Ideas are a marketplace. May the best ideas win. Nostr allows me to speak with people about topics I might not otherwise get a chance to speak about. I never see any pro-communist posts on Twitter. That's a problem because communists also don't see me. I also never saw sex workers talk about anything other than kinky-boinky talk on Twitter. Nostr brings the humanity back to sex workers. Sex workers are people too. They have interesting ideas and take [interesting photos]([take interesting pictures](nostr:note1svl3ne6l7dkxx4gckqsttx24nva7m37ynam7rvgq4zu83u9wl2ks86ahwx). ) On the [What is Money Show](https://fountain.fm/episode/DYPKRSkN11EmYDhrhH0H), Rabble says he wants to have Christians have a Christian-only Nostr network and sex workers to have a sex worker-only network. It's a fun idea, but I'm not convinced this would be a good thing. What if Jesus was on the Christian Nostr, but Mary Magdalen was on sex worker Nostr? I suspect Christians talking to sex workers is not such a bad thing. **What would Jesus do?** Here is a conversation I had with a stripper on nostr. You can read the original [here](nostr:note1wxalrm6tpftrrs9rmzvv4e5gpnamkmfuu6fpwu9gs3wtudeegd7qpd5l0r) but I have reprinted it on the Habla and Substack. I don't believe it's possible for a community or state to abolish private property when the private property can be distilled into 12 secret random words. Ironically, bitcoin does give the means of monetary production to the people, but this is a moot point given that individual people do not have equal ability. Very few people had sufficient knowledge to mine bitcoin when the block reward was 50 bitcoin every 10 minutes. Therefore, even though anybody could technically produce bitcoin blocks, very few people can. The same is true for saving. Even if we could defy human nature with schemes such as this, it would not solve wealth inequality. Most people spend money like drunken sailors. If everyone had the same income that could not be debased or stolen, broke people would still exist because people do not have equal money management skills. That is why I prefer capitalism with a non-socialist monetary system. The United States, contrary to popular belief, is not a capitalist economic system. It's a mixed economy where some people (banks and government) get money without doing any work aside from fudging numbers. A bank does not save capital to buy a house. Banks print money to buy homes and collect rent from homeowners. It's an accounting trick, not capitalism. Here's how capitalism works according to economist, Russ Roberts. https://youtu.be/ljULutAUL7o?si=bLPY5IvwwMQvfXJK npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0 https://mempool.marc26z.com/block/00000000000000000001fa33d3d7750ed315d94e3c1def6512281b33bece333b
@ df478568:2a951e67
2025-02-13 02:04:30In the very early days, Nostr was pretty much troll-free. It was one of my favorite things about it, but I suspected this was only the case because only hardcore bitcoiners were on there. Now that the network is growing, there is more diversity of ideas. Ideology tends to make people mean. Mean people suck, so I try to remain respectful even when I disagree with others. I am not a fan of communism, but enjoy reading other perspectives. I do not wish to censor any speech at all, especially speech I do not agree with. The freedom of speech is not about the First Amendment to me. It's about creating a space that is safe for free speech. Platforms are not a safe space for free speech. The safety of free speech is in peril on platforms. Nostr is a space where people can speak freely in an open Internet-connected society. There is some speech I would rather not see. I wish some people did not say certain things, but I do not want to stop them. If we censor the worst speech, the speech does not go away. It merely goes underground and creates bad speech silos where people hide their true selves and go only speak to people just like them. Censorship is like prison for ideas. Prisoners improve their robbery skills because they exchange ideas with other criminals. It's like a conference for criminals. Fascists get more fascist when they only have permission to talk to fellow fascists. Communists get more communist when they can only talk to other communists. Ideas are a marketplace. May the best ideas win. Nostr allows me to speak with people about topics I might not otherwise get a chance to speak about. I never see any pro-communist posts on Twitter. That's a problem because communists also don't see me. I also never saw sex workers talk about anything other than kinky-boinky talk on Twitter. Nostr brings the humanity back to sex workers. Sex workers are people too. They have interesting ideas and take [interesting photos]([take interesting pictures](nostr:note1svl3ne6l7dkxx4gckqsttx24nva7m37ynam7rvgq4zu83u9wl2ks86ahwx). ) On the [What is Money Show](https://fountain.fm/episode/DYPKRSkN11EmYDhrhH0H), Rabble says he wants to have Christians have a Christian-only Nostr network and sex workers to have a sex worker-only network. It's a fun idea, but I'm not convinced this would be a good thing. What if Jesus was on the Christian Nostr, but Mary Magdalen was on sex worker Nostr? I suspect Christians talking to sex workers is not such a bad thing. **What would Jesus do?** Here is a conversation I had with a stripper on nostr. You can read the original [here](nostr:note1wxalrm6tpftrrs9rmzvv4e5gpnamkmfuu6fpwu9gs3wtudeegd7qpd5l0r) but I have reprinted it on the Habla and Substack. I don't believe it's possible for a community or state to abolish private property when the private property can be distilled into 12 secret random words. Ironically, bitcoin does give the means of monetary production to the people, but this is a moot point given that individual people do not have equal ability. Very few people had sufficient knowledge to mine bitcoin when the block reward was 50 bitcoin every 10 minutes. Therefore, even though anybody could technically produce bitcoin blocks, very few people can. The same is true for saving. Even if we could defy human nature with schemes such as this, it would not solve wealth inequality. Most people spend money like drunken sailors. If everyone had the same income that could not be debased or stolen, broke people would still exist because people do not have equal money management skills. That is why I prefer capitalism with a non-socialist monetary system. The United States, contrary to popular belief, is not a capitalist economic system. It's a mixed economy where some people (banks and government) get money without doing any work aside from fudging numbers. A bank does not save capital to buy a house. Banks print money to buy homes and collect rent from homeowners. It's an accounting trick, not capitalism. Here's how capitalism works according to economist, Russ Roberts. https://youtu.be/ljULutAUL7o?si=bLPY5IvwwMQvfXJK npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0 https://mempool.marc26z.com/block/00000000000000000001fa33d3d7750ed315d94e3c1def6512281b33bece333b @ 16d11430:61640947
2025-01-21 20:40:22In a world drowning in Monopoly money, where people celebrate government-mandated inflation as "economic growth," it takes a special kind of clarity—nay, cynicism—to rise above the fiat circus. This is your guide to shedding your fiat f**ks and embracing the serene chaos of sound money, all while laughing at the absurdity of a world gone fiat-mad. --- 1. Don’t Feed the Clowns You know the clowns I’m talking about: central bankers in their tailored suits and smug smirks, wielding "tools" like interest rates and quantitative easing. Their tools are as real as a magician's wand, conjuring trillions of dollars out of thin air to keep their Ponzi economy afloat. Rule #1: Don’t engage. If a clown offers you a hot take about the "strength of the dollar," smile, nod, and silently wonder how many cups of coffee their paycheck buys this month. Spoiler: fewer than last month. --- 2. Turn Off the Fiat News Do you really need another breathless headline about the next trillion-dollar deficit? Or the latest clickbait on why you should care about the stock market's emotional rollercoaster? Mainstream media exists to distract you, to keep you tethered to their illusion of importance. Turn it off. Replace it with something sound, like the Bitcoin whitepaper. Or Nietzsche. At least Nietzsche knew we were doomed. --- 3. Mock Their Inflationary Gospel Fiat apologists will tell you that inflation is "necessary" and that 2% a year is a "healthy target." Sure, because a little robbery every year keeps society functioning, right? Ask them this: "If 2% is healthy, why not 20%? Why not 200%? Why not Venezuela?" Fiat logic is like a bad acid trip: entertaining at first, but it quickly spirals into existential horror. --- 4. Celebrate the Fiat Freakshow Sometimes, the best way to resist the fiat clown show is to revel in its absurdity. Watch politicians print money like teenagers running up a credit card bill at Hot Topic, then watch the economists applaud it as "stimulus." It’s performance art, really. Andy Warhol could never. --- 5. Build in the Chaos While the fiat world burns, Bitcoiners build. This is the ultimate "not giving a fiat f**k" move: creating a parallel economy, one satoshi at a time. Run your Lightning node, stack sats, and laugh as the fiat circus consumes itself in a flaming pile of its own debt. Let them argue about who gets to rearrange the deck chairs on the Titanic. You’re busy designing lifeboats. --- 6. Adopt a Fiat-Free Lifestyle Fiat-free living means minimizing your entanglement with their clown currency. Buy meat, not ETFs. Trade skills, not IOUs. Tip your barber in Bitcoin and ask if your landlord accepts Lightning. If they say no, chuckle and say, “You’ll learn soon enough.” Every satoshi spent in the real economy is a slap in the face to the fiat overlords. --- 7. Find the Humor in Collapse Here’s the thing: the fiat system is unsustainable. You know it, I know it, even the clowns know it. The whole charade is destined to collapse under its own weight. When it does, find solace in the absurdity of it all. Imagine the central bankers explaining hyperinflation to the public: "Turns out we can't print infinity after all." Pure comedy gold. --- 8. Stay Ruthlessly Optimistic Despite the doom and gloom, there’s hope. Bitcoin is hope. It’s the lifeboat for humanity, the cheat code to escape the fiat matrix. Cynicism doesn’t mean nihilism; it means seeing the rot for what it is and choosing to build something better. So, don’t just reject the fiat clown show—replace it. Create a world where money is sound, transactions are sovereign, and wealth is measured in energy, not debt. --- Final Thought: Burn the Tent Down Aldous Huxley once envisioned a dystopia where people are so distracted by their own hedonistic consumption that they don’t realize they’re enslaved. Sound familiar? The fiat clown show is Brave New World on steroids, a spectacle designed to keep you pacified while your wealth evaporates. But here’s the punchline: they can only enslave you if you care. By rejecting their system, you strip them of their power. So let them juggle their debts, inflate their bubbles, and print their trillions. You’ve got Bitcoin, and Bitcoin doesn’t give a fiat f**k. Welcome to the satirical resistance. Now go stack some sats.
@ 16d11430:61640947
2025-01-21 20:40:22In a world drowning in Monopoly money, where people celebrate government-mandated inflation as "economic growth," it takes a special kind of clarity—nay, cynicism—to rise above the fiat circus. This is your guide to shedding your fiat f**ks and embracing the serene chaos of sound money, all while laughing at the absurdity of a world gone fiat-mad. --- 1. Don’t Feed the Clowns You know the clowns I’m talking about: central bankers in their tailored suits and smug smirks, wielding "tools" like interest rates and quantitative easing. Their tools are as real as a magician's wand, conjuring trillions of dollars out of thin air to keep their Ponzi economy afloat. Rule #1: Don’t engage. If a clown offers you a hot take about the "strength of the dollar," smile, nod, and silently wonder how many cups of coffee their paycheck buys this month. Spoiler: fewer than last month. --- 2. Turn Off the Fiat News Do you really need another breathless headline about the next trillion-dollar deficit? Or the latest clickbait on why you should care about the stock market's emotional rollercoaster? Mainstream media exists to distract you, to keep you tethered to their illusion of importance. Turn it off. Replace it with something sound, like the Bitcoin whitepaper. Or Nietzsche. At least Nietzsche knew we were doomed. --- 3. Mock Their Inflationary Gospel Fiat apologists will tell you that inflation is "necessary" and that 2% a year is a "healthy target." Sure, because a little robbery every year keeps society functioning, right? Ask them this: "If 2% is healthy, why not 20%? Why not 200%? Why not Venezuela?" Fiat logic is like a bad acid trip: entertaining at first, but it quickly spirals into existential horror. --- 4. Celebrate the Fiat Freakshow Sometimes, the best way to resist the fiat clown show is to revel in its absurdity. Watch politicians print money like teenagers running up a credit card bill at Hot Topic, then watch the economists applaud it as "stimulus." It’s performance art, really. Andy Warhol could never. --- 5. Build in the Chaos While the fiat world burns, Bitcoiners build. This is the ultimate "not giving a fiat f**k" move: creating a parallel economy, one satoshi at a time. Run your Lightning node, stack sats, and laugh as the fiat circus consumes itself in a flaming pile of its own debt. Let them argue about who gets to rearrange the deck chairs on the Titanic. You’re busy designing lifeboats. --- 6. Adopt a Fiat-Free Lifestyle Fiat-free living means minimizing your entanglement with their clown currency. Buy meat, not ETFs. Trade skills, not IOUs. Tip your barber in Bitcoin and ask if your landlord accepts Lightning. If they say no, chuckle and say, “You’ll learn soon enough.” Every satoshi spent in the real economy is a slap in the face to the fiat overlords. --- 7. Find the Humor in Collapse Here’s the thing: the fiat system is unsustainable. You know it, I know it, even the clowns know it. The whole charade is destined to collapse under its own weight. When it does, find solace in the absurdity of it all. Imagine the central bankers explaining hyperinflation to the public: "Turns out we can't print infinity after all." Pure comedy gold. --- 8. Stay Ruthlessly Optimistic Despite the doom and gloom, there’s hope. Bitcoin is hope. It’s the lifeboat for humanity, the cheat code to escape the fiat matrix. Cynicism doesn’t mean nihilism; it means seeing the rot for what it is and choosing to build something better. So, don’t just reject the fiat clown show—replace it. Create a world where money is sound, transactions are sovereign, and wealth is measured in energy, not debt. --- Final Thought: Burn the Tent Down Aldous Huxley once envisioned a dystopia where people are so distracted by their own hedonistic consumption that they don’t realize they’re enslaved. Sound familiar? The fiat clown show is Brave New World on steroids, a spectacle designed to keep you pacified while your wealth evaporates. But here’s the punchline: they can only enslave you if you care. By rejecting their system, you strip them of their power. So let them juggle their debts, inflate their bubbles, and print their trillions. You’ve got Bitcoin, and Bitcoin doesn’t give a fiat f**k. Welcome to the satirical resistance. Now go stack some sats. @ 6be5cc06:5259daf0
2025-01-21 01:51:46## Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas. Satoshi Nakamoto satoshin@gmx.com www.bitcoin.org --- ### Resumo O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado **gasto duplo**, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações. As transações são registradas em um livro público chamado **blockchain**, protegido por uma técnica chamada **Prova de Trabalho**. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira. Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu. --- ### 1. Introdução Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em **confiança**. Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável. Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável. O que precisamos é de um **sistema de pagamento eletrônico baseado em provas matemáticas**, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas. Neste documento, apresentamos o **Bitcoin**, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques. --- ### 2. Transações Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital. #### O que é uma assinatura digital? Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso. #### Como funciona na prática? Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário: 1. A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1. 2. Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2. 3. Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda. #### Resolvendo o problema do gasto duplo Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro. O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain. #### Por que isso é importante? Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes. --- ### 3. Servidor Timestamp Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica. Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público. Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain. Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada. O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin. --- ### 4. Prova-de-Trabalho Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente. A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita. Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain. A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos. Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional. --- ### 5. Rede A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são: 1. **Transmissão de Transações**: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la. 2. **Coleta de Transações em Blocos**: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain). 3. **Prova-de-Trabalho**: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil. 4. **Envio do Bloco Resolvido**: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede. 5. **Validação do Bloco**: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos. 6. **Construção do Próximo Bloco**: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia. #### Resolução de Conflitos e Escolha da Cadeia Mais Longa Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia. #### Tolerância a Falhas A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido. Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central. --- ### 6. Incentivo O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação. #### Recompensa por Mineração Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho. #### Taxas de Transação Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo. #### Incentivo à Honestidade O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas: 1. Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos. 2. Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas. A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema. Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo. --- ### 7. Recuperação do Espaço em Disco Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações. Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados. Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados. Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo. --- ### 8. Verificação de Pagamento Simplificada É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada. Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação. A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede. Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável. --- ### 9. Combinando e Dividindo Valor No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor. #### Entradas e Saídas Cada transação no Bitcoin é composta por: - **Entradas**: Representam os valores recebidos em transações anteriores. - **Saídas**: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente. Normalmente, uma transação contém: - Uma única entrada com valor suficiente para cobrir o pagamento. - Ou várias entradas combinadas para atingir o valor necessário. O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como **troco**. #### Exemplo Prático Imagine que você tem duas entradas: 1. 0,03 BTC 2. 0,07 BTC Se deseja enviar 0,08 BTC para alguém, a transação terá: - **Entrada**: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC). - **Saídas**: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC). Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente. #### Difusão e Simplificação A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade. --- ### 10. Privacidade O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando **chaves públicas anônimas**, que desvinculam diretamente as transações das identidades das partes envolvidas. #### Fluxo de Informação - No **modelo tradicional**, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário. - No **Bitcoin**, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não. #### Protegendo a Privacidade Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas: 1. **Chaves Públicas Anônimas**: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único. 2. **Prevenção de Ligação**: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário. #### Riscos de Ligação Embora a privacidade seja fortalecida, alguns riscos permanecem: - Transações **multi-entrada** podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total. - O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas. --- ### 11. Cálculos Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito. Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira. Mas isso é extremamente difícil. #### Como o Ataque Funciona Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido. - Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira. - O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida. Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente. #### A Corrida Entre Cadeias Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos. Suponha que: - A rede honesta tem **80% do poder computacional** (ou seja, resolve 8 de cada 10 quebra-cabeças). - O atacante tem **20% do poder computacional** (ou seja, resolve 2 de cada 10 quebra-cabeças). Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar. #### Por Que o Ataque Fica Cada Vez Mais Improvável? Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos: P = (q/p)^z - **q** é o poder computacional do atacante (20%, ou 0,2). - **p** é o poder computacional da rede honesta (80%, ou 0,8). - **z** é a diferença de blocos entre a cadeia honesta e a cadeia do atacante. Se o atacante está 5 blocos atrás (z = 5): P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%) Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável. Se ele estiver 10 blocos atrás (z = 10): P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%). Neste caso, as chances de sucesso são praticamente **nulas**. #### Um Exemplo Simples Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível. No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática. #### Por Que Tudo Isso é Seguro? - **A probabilidade de sucesso do atacante diminui exponencialmente.** Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema. - **A cadeia verdadeira (honesta) está protegida pela força da rede.** Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar. #### E Se o Atacante Tentar Continuar? O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil. Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso. --- ### 12. Conclusão Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos. --- Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
@ 6be5cc06:5259daf0
2025-01-21 01:51:46## Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas. Satoshi Nakamoto satoshin@gmx.com www.bitcoin.org --- ### Resumo O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado **gasto duplo**, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações. As transações são registradas em um livro público chamado **blockchain**, protegido por uma técnica chamada **Prova de Trabalho**. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira. Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu. --- ### 1. Introdução Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em **confiança**. Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável. Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável. O que precisamos é de um **sistema de pagamento eletrônico baseado em provas matemáticas**, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas. Neste documento, apresentamos o **Bitcoin**, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques. --- ### 2. Transações Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital. #### O que é uma assinatura digital? Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso. #### Como funciona na prática? Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário: 1. A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1. 2. Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2. 3. Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda. #### Resolvendo o problema do gasto duplo Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro. O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain. #### Por que isso é importante? Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes. --- ### 3. Servidor Timestamp Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica. Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público. Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain. Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada. O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin. --- ### 4. Prova-de-Trabalho Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente. A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita. Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain. A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos. Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional. --- ### 5. Rede A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são: 1. **Transmissão de Transações**: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la. 2. **Coleta de Transações em Blocos**: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain). 3. **Prova-de-Trabalho**: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil. 4. **Envio do Bloco Resolvido**: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede. 5. **Validação do Bloco**: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos. 6. **Construção do Próximo Bloco**: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia. #### Resolução de Conflitos e Escolha da Cadeia Mais Longa Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia. #### Tolerância a Falhas A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido. Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central. --- ### 6. Incentivo O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação. #### Recompensa por Mineração Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho. #### Taxas de Transação Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo. #### Incentivo à Honestidade O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas: 1. Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos. 2. Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas. A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema. Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo. --- ### 7. Recuperação do Espaço em Disco Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações. Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados. Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados. Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo. --- ### 8. Verificação de Pagamento Simplificada É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada. Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação. A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede. Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável. --- ### 9. Combinando e Dividindo Valor No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor. #### Entradas e Saídas Cada transação no Bitcoin é composta por: - **Entradas**: Representam os valores recebidos em transações anteriores. - **Saídas**: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente. Normalmente, uma transação contém: - Uma única entrada com valor suficiente para cobrir o pagamento. - Ou várias entradas combinadas para atingir o valor necessário. O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como **troco**. #### Exemplo Prático Imagine que você tem duas entradas: 1. 0,03 BTC 2. 0,07 BTC Se deseja enviar 0,08 BTC para alguém, a transação terá: - **Entrada**: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC). - **Saídas**: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC). Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente. #### Difusão e Simplificação A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade. --- ### 10. Privacidade O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando **chaves públicas anônimas**, que desvinculam diretamente as transações das identidades das partes envolvidas. #### Fluxo de Informação - No **modelo tradicional**, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário. - No **Bitcoin**, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não. #### Protegendo a Privacidade Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas: 1. **Chaves Públicas Anônimas**: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único. 2. **Prevenção de Ligação**: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário. #### Riscos de Ligação Embora a privacidade seja fortalecida, alguns riscos permanecem: - Transações **multi-entrada** podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total. - O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas. --- ### 11. Cálculos Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito. Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira. Mas isso é extremamente difícil. #### Como o Ataque Funciona Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido. - Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira. - O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida. Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente. #### A Corrida Entre Cadeias Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos. Suponha que: - A rede honesta tem **80% do poder computacional** (ou seja, resolve 8 de cada 10 quebra-cabeças). - O atacante tem **20% do poder computacional** (ou seja, resolve 2 de cada 10 quebra-cabeças). Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar. #### Por Que o Ataque Fica Cada Vez Mais Improvável? Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos: P = (q/p)^z - **q** é o poder computacional do atacante (20%, ou 0,2). - **p** é o poder computacional da rede honesta (80%, ou 0,8). - **z** é a diferença de blocos entre a cadeia honesta e a cadeia do atacante. Se o atacante está 5 blocos atrás (z = 5): P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%) Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável. Se ele estiver 10 blocos atrás (z = 10): P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%). Neste caso, as chances de sucesso são praticamente **nulas**. #### Um Exemplo Simples Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível. No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática. #### Por Que Tudo Isso é Seguro? - **A probabilidade de sucesso do atacante diminui exponencialmente.** Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema. - **A cadeia verdadeira (honesta) está protegida pela força da rede.** Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar. #### E Se o Atacante Tentar Continuar? O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil. Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso. --- ### 12. Conclusão Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos. --- Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf @ ac6f9572:8a6853dd
2025-02-13 01:56:23 Date: 02/12/2025 One of the most efficient options to expand your knowledge and truly connect with people actively working in the space is through direct interactions, whether they’re happening at large conferences or smaller, semi-official meetups. But let’s be honest: finding all meaningful events can be a mess. Take, for example, the '[BTC Events Map](https://docs.google.com/spreadsheets/d/1oni0QAHb2XYOL5gFVKHHGhG8w_HY5GDGBhdQ4SSrCZg/edit?gid=0&ref=europeanbitcoiners.com#gid=0),’ which already lists over 550 Bitcoin-only gatherings worldwide. This simple but very useful resource, put together by Satlantis, can help many of us plan our trips throughout the year. However, if you don’t know about its existence and rely solely on a search engine—whether Google or Brave—you’ll likely end up frustrated (and unfortunately missing many great opportunities to meet with others and learn). Search for '_bitcoin events_,' and you’ll get a mix of irrelevant crypto, fintech, and Web3 results, with Bitcoin-related stuff buried somewhere in the middle, if at all.. Well, it’s really tough to find what you’re actually looking for. That’s why word of mouth and trusted communities are so important. Sometimes, the best way to hear about an event is directly from people you know. **One of those that flew under my radar was** [**SatsNFacts**](https://satsnfacts.btc.pub/?ref=europeanbitcoiners.com)**.** It wasn’t listed on many typical event aggregators or any big news-promo sites. It mostly spread peer-to-peer and through the main channels on [Nostr](https://njump.me/npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx?ref=europeanbitcoiners.com). I was ‘_lucky_’ enough to hear about it just in time to plan the trip from Europe to Thailand. Now, I’d like to briefly share my experience with you—everything that, in my opinion, made this event truly stand out. **A Journey to Southeast Asia: Where Builders and Artists Collide.** -------------------------------------------------------------------- Approximately 10,176 kilometers, 14 hours of travel, and finally three days spent at SatsNFacts—"Thailand’s first Bitcoin Technical Unconference”. The event ran from February 8 to 10 in Chiang Mai (the largest city in northern Thailand). Held at Weave Artisan Society, a 700 sq.m venue that used to be an ice factory, it smoothly combined pleasant outdoors with an industrial-style, two-floor indoor area, creating a unique and very practical setup. While its was billed as a “_Technical Unconference_,” in practice it nicely connected the developer-based ecosystem with different aspects of culture and art. Each day, from 10 am to 6 pm, the agenda—shaped directly by attendees—was packed with various presentations, group chats, learning session, hackathons, and actionable workshops. With many options available (around 10-20 topics per day), I couldn’t attend everything, but here are a few more technical sessions I joined and found especially worthwhile: * **Liana Workshop** (long-term security, recovery, and inheritance), * **TollGates** ([streaming sats for internet access](https://primal.net/e/naddr1qvzqqqr4gupzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68qq2nz63h0969vn2xwse9j3n5ge4xsdr2ddc4j0g960h?ref=europeanbitcoiners.com)), * **Open Vault** (enterprise wallet interface), * **Yaki Honne** ([decentralized media](https://yakihonne.com/?ref=europeanbitcoiners.com)), * **Nostr Proxies** (Epoxy, WebSocket and relay monetization). * **Silent payments** (simplified payment experiences without compromising privacy). As mentioned earlier, SatsNFacts wasn’t just about Bitcoin tech. Some topics focused on community aspects as well. Two discussions I joined highlighted Bitcoin adoption ⚡ in for example Bali and Thailand, showing how sound money, integrity, and consistent work can solve real problems in these regions. Impressive stuff! Here you can learn more: * [HuaiPhueng](https://geyser.fund/project/huaiphuengproject?hero=geyser&ref=europeanbitcoiners.com) on Geyser + "Bitcoin City" (their [short video](https://www.youtube.com/watch?feature=shared&v=211meP4liIo&ref=europeanbitcoiners.com)). * Bitcoin Indonesia & Bitcoin House Bali ([all in one on GitHub](https://github.com/bitcoinindo21?ref=europeanbitcoiners.com)) Now, the art gallery, to continue with less technical aspects of SatsNFacts 🎨 This nicely-organized space located on the ground floor, near cozy coworking and networking spots, was for me a real gem. Indeed, adding a creative vibe to the entire event. Around 30 unique works from local and international artists were on display, all inspired by themes of freedom and privacy. Though I don’t see myself as a typical _'artist_', I was honored to have some of my own pieces exhibited there as well (a short video below). * * * One of the highlights was meeting local Thai artists, especially [Siritravelsketch](https://njump.me/npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu?ref=europeanbitcoiners.com), who travelled six hours by train just one way to attend two days of the event. Her stunning paintings, created using just a bamboo stick and ink, are deeply inspired by Thai architecture and culture. While some of her pre-prepared pieces hung in the gallery, she also painted a few new works on the spot during her visit. Truly spectacular!  * * * I also had the chance to reconnect with [Satoshi Builds](https://njump.me/npub19m7m3rs66pfdn4ewhrm8slh60ukyxgrylaa03m73wa40j39lc03syq4gfu?ref=europeanbitcoiners.com), who made many great sketches during this event, and with [BitPopArt](https://njump.me/npub1gwa27rpgum8mr9d30msg8cv7kwj2lhav2nvmdwh3wqnsa5vnudxqlta2sz?ref=europeanbitcoiners.com), a Dutch artist who, just like me, chosen a nomadic lifestyle yet has been clearly considering Thailand his 'second home' as well for several years now. By the way, ✍️ here's his short summary of the event, focusing more on the artistic side of SatsNFacts: "[Art exhibition in Chiang Mai](https://bitpopart.com/2025/02/11/art-exhibition-in-chiang-mai/?ref=europeanbitcoiners.com)". All in all, spending my time in many meaningful conversations and seeing so many deep artworks in one place filled me with hope and positive energy. THANK YOU, EVERYONE!  * * * (presented artworks by for example: [Agi Choote](https://njump.me/npub1tlacuxmtv2wqud9qz0ujnr4mqavmnz3ayspfj93jr40tgf2mvu6seax3y7?ref=europeanbitcoiners.com), [Samhain](https://njump.me/npub1df47g7a39usamq83aula72zdz23fx9xw5rrfmd0v6p9t20n5u0ss2eqez9?ref=europeanbitcoiners.com), [Zed Erwan](https://njump.me/npub1r2sah0htqnw7xrs70gq00m48vp25neu8ym2n2ghrny92dqqf7sest8hth0?ref=europeanbitcoiners.com), [Existing Sprinkles](https://njump.me/npub1f5kc2agn63ecv2ua4909z9ahgmr2x9263na36jh6r908ql0926jq3nvk2u?ref=europeanbitcoiners.com), AZA 21m, BitPopArt.) * * * Mr. Rabbit in Thailand... ------------------------- Monday, the final evening, and SatsNFacts got one more item on its agenda rooted in creative expression and independent art. Representing [Bitcoin FilmFest](https://x.com/bitcoinfilmfest?ref=europeanbitcoiners.com) (a grassroots project created by an amazing group of freedom fighters and activists 🐇🧡), since I was the only one from our team in Thailand, in one of the rooms upstairs, I put together a mini cinematic experience. Seven trailers and eleven shorts, including for example: * NO MORE INFLATION, HUMMINGBIRD, PARALLEL SPACE, UNBANKABLE, THE LEGEND OF LANDI (🎬 some of the trailers). * BITCOIN A NEW HOPE, SATOSHI NAKAMOTO - THE CREATOR OF BITCOIN, MAXIS CLUB SHOW - CHAPTER ONE, THE GREATEST HEIST IN HISTORY, HODL, THE ANATOMY OF BITCOIN – GENESIS BLOCK (📺 some of the presented shorts) With around 10-15 participants, the response was positive, and we ended up spending an extra 10-maybe-20 minutes discussing the challenges and opportunities in Bitcoin-powered filmmaking, as well as the upcoming edition of [BFF25](https://bitcoinfilmfest.com/bff25/?ref=europeanbitcoiners.com) (the annual festival we're organizing this May in Warsaw, Poland).  **Substance Over Hype. Gatherings That Matter.** ------------------------------------------------ SatsNFacts made a solid reminder that Bitcoin events can help build a truly sovereign future while bringing together developers and artistic souls alike. The mix of technical depth and creative energy—free from the shiny gossip that floods many social channels—made it a truly meaningful experience. > SatsNFacts set a high standard, and I hope to see more events like it in the future. More unconferences, more cultural and community-driven gatherings. **Here's to more signal, less noise!!!** Big congrats to everyone who made the first SatsNFacts happen 👏 Respect especially to the organizers! You pulled off something truly special! * * * _BTC Your Mind. Let it Beat._ _Şela_ @AZA_21M 💡 Did you enjoy this article? Zap me some sats. No amount is small :) Lightning wallet: `aza21m@getalby.com` - - - Original Article: https://europeanbitcoiners.com/sats-and-facts-short-coverage-of-the-first-bitcoin-unconference-in-thailand/ #english #opinion #events #bitcoin #nostr #freedom #conference #siamstr #asia #thailand
@ ac6f9572:8a6853dd
2025-02-13 01:56:23 Date: 02/12/2025 One of the most efficient options to expand your knowledge and truly connect with people actively working in the space is through direct interactions, whether they’re happening at large conferences or smaller, semi-official meetups. But let’s be honest: finding all meaningful events can be a mess. Take, for example, the '[BTC Events Map](https://docs.google.com/spreadsheets/d/1oni0QAHb2XYOL5gFVKHHGhG8w_HY5GDGBhdQ4SSrCZg/edit?gid=0&ref=europeanbitcoiners.com#gid=0),’ which already lists over 550 Bitcoin-only gatherings worldwide. This simple but very useful resource, put together by Satlantis, can help many of us plan our trips throughout the year. However, if you don’t know about its existence and rely solely on a search engine—whether Google or Brave—you’ll likely end up frustrated (and unfortunately missing many great opportunities to meet with others and learn). Search for '_bitcoin events_,' and you’ll get a mix of irrelevant crypto, fintech, and Web3 results, with Bitcoin-related stuff buried somewhere in the middle, if at all.. Well, it’s really tough to find what you’re actually looking for. That’s why word of mouth and trusted communities are so important. Sometimes, the best way to hear about an event is directly from people you know. **One of those that flew under my radar was** [**SatsNFacts**](https://satsnfacts.btc.pub/?ref=europeanbitcoiners.com)**.** It wasn’t listed on many typical event aggregators or any big news-promo sites. It mostly spread peer-to-peer and through the main channels on [Nostr](https://njump.me/npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx?ref=europeanbitcoiners.com). I was ‘_lucky_’ enough to hear about it just in time to plan the trip from Europe to Thailand. Now, I’d like to briefly share my experience with you—everything that, in my opinion, made this event truly stand out. **A Journey to Southeast Asia: Where Builders and Artists Collide.** -------------------------------------------------------------------- Approximately 10,176 kilometers, 14 hours of travel, and finally three days spent at SatsNFacts—"Thailand’s first Bitcoin Technical Unconference”. The event ran from February 8 to 10 in Chiang Mai (the largest city in northern Thailand). Held at Weave Artisan Society, a 700 sq.m venue that used to be an ice factory, it smoothly combined pleasant outdoors with an industrial-style, two-floor indoor area, creating a unique and very practical setup. While its was billed as a “_Technical Unconference_,” in practice it nicely connected the developer-based ecosystem with different aspects of culture and art. Each day, from 10 am to 6 pm, the agenda—shaped directly by attendees—was packed with various presentations, group chats, learning session, hackathons, and actionable workshops. With many options available (around 10-20 topics per day), I couldn’t attend everything, but here are a few more technical sessions I joined and found especially worthwhile: * **Liana Workshop** (long-term security, recovery, and inheritance), * **TollGates** ([streaming sats for internet access](https://primal.net/e/naddr1qvzqqqr4gupzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68qq2nz63h0969vn2xwse9j3n5ge4xsdr2ddc4j0g960h?ref=europeanbitcoiners.com)), * **Open Vault** (enterprise wallet interface), * **Yaki Honne** ([decentralized media](https://yakihonne.com/?ref=europeanbitcoiners.com)), * **Nostr Proxies** (Epoxy, WebSocket and relay monetization). * **Silent payments** (simplified payment experiences without compromising privacy). As mentioned earlier, SatsNFacts wasn’t just about Bitcoin tech. Some topics focused on community aspects as well. Two discussions I joined highlighted Bitcoin adoption ⚡ in for example Bali and Thailand, showing how sound money, integrity, and consistent work can solve real problems in these regions. Impressive stuff! Here you can learn more: * [HuaiPhueng](https://geyser.fund/project/huaiphuengproject?hero=geyser&ref=europeanbitcoiners.com) on Geyser + "Bitcoin City" (their [short video](https://www.youtube.com/watch?feature=shared&v=211meP4liIo&ref=europeanbitcoiners.com)). * Bitcoin Indonesia & Bitcoin House Bali ([all in one on GitHub](https://github.com/bitcoinindo21?ref=europeanbitcoiners.com)) Now, the art gallery, to continue with less technical aspects of SatsNFacts 🎨 This nicely-organized space located on the ground floor, near cozy coworking and networking spots, was for me a real gem. Indeed, adding a creative vibe to the entire event. Around 30 unique works from local and international artists were on display, all inspired by themes of freedom and privacy. Though I don’t see myself as a typical _'artist_', I was honored to have some of my own pieces exhibited there as well (a short video below). * * * One of the highlights was meeting local Thai artists, especially [Siritravelsketch](https://njump.me/npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu?ref=europeanbitcoiners.com), who travelled six hours by train just one way to attend two days of the event. Her stunning paintings, created using just a bamboo stick and ink, are deeply inspired by Thai architecture and culture. While some of her pre-prepared pieces hung in the gallery, she also painted a few new works on the spot during her visit. Truly spectacular!  * * * I also had the chance to reconnect with [Satoshi Builds](https://njump.me/npub19m7m3rs66pfdn4ewhrm8slh60ukyxgrylaa03m73wa40j39lc03syq4gfu?ref=europeanbitcoiners.com), who made many great sketches during this event, and with [BitPopArt](https://njump.me/npub1gwa27rpgum8mr9d30msg8cv7kwj2lhav2nvmdwh3wqnsa5vnudxqlta2sz?ref=europeanbitcoiners.com), a Dutch artist who, just like me, chosen a nomadic lifestyle yet has been clearly considering Thailand his 'second home' as well for several years now. By the way, ✍️ here's his short summary of the event, focusing more on the artistic side of SatsNFacts: "[Art exhibition in Chiang Mai](https://bitpopart.com/2025/02/11/art-exhibition-in-chiang-mai/?ref=europeanbitcoiners.com)". All in all, spending my time in many meaningful conversations and seeing so many deep artworks in one place filled me with hope and positive energy. THANK YOU, EVERYONE!  * * * (presented artworks by for example: [Agi Choote](https://njump.me/npub1tlacuxmtv2wqud9qz0ujnr4mqavmnz3ayspfj93jr40tgf2mvu6seax3y7?ref=europeanbitcoiners.com), [Samhain](https://njump.me/npub1df47g7a39usamq83aula72zdz23fx9xw5rrfmd0v6p9t20n5u0ss2eqez9?ref=europeanbitcoiners.com), [Zed Erwan](https://njump.me/npub1r2sah0htqnw7xrs70gq00m48vp25neu8ym2n2ghrny92dqqf7sest8hth0?ref=europeanbitcoiners.com), [Existing Sprinkles](https://njump.me/npub1f5kc2agn63ecv2ua4909z9ahgmr2x9263na36jh6r908ql0926jq3nvk2u?ref=europeanbitcoiners.com), AZA 21m, BitPopArt.) * * * Mr. Rabbit in Thailand... ------------------------- Monday, the final evening, and SatsNFacts got one more item on its agenda rooted in creative expression and independent art. Representing [Bitcoin FilmFest](https://x.com/bitcoinfilmfest?ref=europeanbitcoiners.com) (a grassroots project created by an amazing group of freedom fighters and activists 🐇🧡), since I was the only one from our team in Thailand, in one of the rooms upstairs, I put together a mini cinematic experience. Seven trailers and eleven shorts, including for example: * NO MORE INFLATION, HUMMINGBIRD, PARALLEL SPACE, UNBANKABLE, THE LEGEND OF LANDI (🎬 some of the trailers). * BITCOIN A NEW HOPE, SATOSHI NAKAMOTO - THE CREATOR OF BITCOIN, MAXIS CLUB SHOW - CHAPTER ONE, THE GREATEST HEIST IN HISTORY, HODL, THE ANATOMY OF BITCOIN – GENESIS BLOCK (📺 some of the presented shorts) With around 10-15 participants, the response was positive, and we ended up spending an extra 10-maybe-20 minutes discussing the challenges and opportunities in Bitcoin-powered filmmaking, as well as the upcoming edition of [BFF25](https://bitcoinfilmfest.com/bff25/?ref=europeanbitcoiners.com) (the annual festival we're organizing this May in Warsaw, Poland).  **Substance Over Hype. Gatherings That Matter.** ------------------------------------------------ SatsNFacts made a solid reminder that Bitcoin events can help build a truly sovereign future while bringing together developers and artistic souls alike. The mix of technical depth and creative energy—free from the shiny gossip that floods many social channels—made it a truly meaningful experience. > SatsNFacts set a high standard, and I hope to see more events like it in the future. More unconferences, more cultural and community-driven gatherings. **Here's to more signal, less noise!!!** Big congrats to everyone who made the first SatsNFacts happen 👏 Respect especially to the organizers! You pulled off something truly special! * * * _BTC Your Mind. Let it Beat._ _Şela_ @AZA_21M 💡 Did you enjoy this article? Zap me some sats. No amount is small :) Lightning wallet: `aza21m@getalby.com` - - - Original Article: https://europeanbitcoiners.com/sats-and-facts-short-coverage-of-the-first-bitcoin-unconference-in-thailand/ #english #opinion #events #bitcoin #nostr #freedom #conference #siamstr #asia #thailand @ 50809a53:e091f164
2025-01-20 22:30:01For starters, anyone who is interested in curating and managing "notes, lists, bookmarks, kind-1 events, or other stuff" should watch this video: https://youtu.be/XRpHIa-2XCE Now, assuming you have watched it, I will proceed assuming you are aware of many of the applications that exist for a very similar purpose. I'll break them down further, following a similar trajectory in order of how I came across them, and a bit about my own path on this journey. We'll start way back in the early 2000s, before Bitcoin existed. We had https://zim-wiki.org/ It is tried and true, and to this day stands to present an option for people looking for a very simple solution to a potentially complex problem. Zim-Wiki works. But it is limited. Let's step into the realm of proprietary. Obsidian, Joplin, and LogSeq. The first two are entirely cloud-operative applications, with more of a focus on the true benefit of being a paid service. I will assume anyone reading this is capable of exploring the marketing of these applications, or trying their freemium product, to get a feeling for what they are capable of. I bring up Obsidian because it is very crucial to understand the market placement of publication. We know social media handles the 'hosting' problem of publishing notes "and other stuff" by harvesting data and making deals with advertisers. But- what Obsidian has evolved to offer is a full service known as 'publish'. This means users can stay in the proprietary pipeline, "from thought to web." all for $8/mo. See: https://obsidian.md/publish THIS IS NOSTR'S PRIMARY COMPETITION. WE ARE HERE TO DISRUPT THIS MARKET, WITH NOTES AND OTHER STUFF. WITH RELAYS. WITH THE PROTOCOL. Now, on to Joplin. I have never used this, because I opted to study the FOSS market and stayed free of any reliance on a paid solution. Many people like Joplin, and I gather the reason is because it has allowed itself to be flexible and good options that integrate with Joplin seems to provide good solutions for users who need that functionality. I see Nostr users recommending Joplin, so I felt it was worthwhile to mention as a case-study option. I myself need to investigate it more, but have found comfort in other solutions. LogSeq - This is my "other solutions." It seems to be trapped in its proprietary web of funding and constraint. I use it because it turns my desktop into a power-house of note archival. But by using it- I AM TRAPPED TOO. This means LogSeq is by no means a working solution for Nostr users who want a long-term archival option. But the trap is not a cage. It's merely a box. My notes can be exported to other applications with graphing and node-based information structure. Specifically, I can export these notes to: - Text - OPML - HTML - and, PNG, for whatever that is worth. Let's try out the PNG option, just for fun. Here's an exported PNG of my "Games on Nostr" list, which has long been abandoned. I once decided to poll some CornyChat users to see what games they enjoyed- and I documented them in a LogSeq page for my own future reference. You can see it here: https://i.postimg.cc/qMBPDTwr/image.png This is a very simple example of how a single "page" or "list" in LogSeq can be multipurpose. It is a small list, with multiple "features" or variables at play. First, I have listed out a variety of complex games that might make sense with "multiplayer" identification that relies on our npubs or nip-05 addresses to aggregate user data. We can ALL imagine playing games like Tetris, Snake, or Catan together with our Nostr identities. But of course we are a long way from breaking into the video game market. On a mostly irrelevant sidenote- you might notice in my example list, that I seem to be excited about a game called Dot.Hack. I discovered this small game on Itch.io and reached out to the developer on Twitter, in an attempt to purple-pill him, but moreso to inquire about his game. Unfortunately there was no response, even without mention of Nostr. Nonetheless, we pioneer on. You can try the game here: https://propuke.itch.io/planethack So instead let's focus on the structure of "one working list." The middle section of this list is where I polled users, and simply listed out their suggestions. Of course we discussed these before I documented, so it is note a direct result of a poll, but actually a working interaction of poll results! This is crucial because it separates my list from the aggregated data, and implies its relevance/importance. The final section of this ONE list- is the beginnings of where I conceptually connect nostr with video game functionality. You can look at this as the beginning of a new graph, which would be "Video Game Operability With Nostr". These three sections make up one concept within my brain. It exists in other users' brains too- but of course they are not as committed to the concept as myself- the one managing the communal discussion. With LogSeq- I can grow and expand these lists. These lists can become graphs. Those graphs can become entire catalogues of information than can be shared across the web. I can replicate this system with bookmarks, ideas, application design, shopping lists, LLM prompting, video/music playlists, friend lists, RELAY lists, the LIST goes ON forever! So where does that lead us? I think it leads us to kind-1 events. We don't have much in the way of "kind-1 event managers" because most developers would agree that "storing kind-1 events locally" is.. at the very least, not so important. But it could be! If only a superapp existed that could interface seamlessly with nostr, yada yada.. we've heard it all before. We aren't getting a superapp before we have microapps. Basically this means frameworking the protocol before worrying about the all-in-one solution. So this article will step away from the deep desire for a Nostr-enabled, Rust-built, FOSS, non-commercialized FREEDOM APP, that will exist one day, we hope. Instead, we will focus on simple attempts of the past. I encourage others to chime in with their experience. Zim-Wiki is foundational. The user constructs pages, and can then develop them into books. LogSeq has the right idea- but is constrained in too many ways to prove to be a working solution at this time. However, it is very much worth experimenting with, and investigating, and modelling ourselves after. https://workflowy.com/ is next on our list. This is great for users who think LogSeq is too complex. They "just want simple notes." Get a taste with WorkFlowy. You will understand why LogSeq is powerful if you see value in WF. I am writing this article in favor of a redesign of LogSeq to be compatible with Nostr. I have been drafting the idea since before Nostr existed- and with Nostr I truly believe it will be possible. So, I will stop to thank everyone who has made Nostr what it is today. I wouldn't be publishing this without you! One app I need to investigate more is Zettlr. I will mention it here for others to either discuss or investigate, as it is also mentioned some in the video I opened with. https://www.zettlr.com/ On my path to finding Nostr, before its inception, was a service called Deta.Space. This was an interesting project, not entirely unique or original, but completely fresh and very beginner-friendly. DETA WAS AN AWESOME CLOUD OS. And we could still design a form of Nostr ecosystem that is managed in this way. But, what we have now is excellent, and going forward I only see "additional" or supplemental. Along the timeline, Deta sunsetted their Space service and launched https://deta.surf/ You might notice they advertise that "This is the future of bookmarks." I have to wonder if perhaps I got through to them that bookmarking was what their ecosystem could empower. While I have not tried Surf, it looks interested, but does not seem to address what I found most valuable about Deta.Space: https://webcrate.app/ WebCrate was an early bookmarking client for Deta.Space which was likely their most popular application. What was amazing about WebCrate was that it delivered "simple bookmarking." At one point I decided to migrate my bookmarks from other apps, like Pocket and WorkFlowy, into WebCrate. This ended up being an awful decision, because WebCrate is no longer being developed. However, to much credit of Deta.Space, my WebCrate instance is still running and completely functional. I have since migrated what I deem important into a local LogSeq graph, so my bookmarks are safe. But, the development of WebCrate is note. WebCrate did not provide a working directory of crates. All creates were contained within a single-level directory. Essentially there were no layers. Just collections of links. This isn't enough for any user to effectively manage their catalogue of notes. With some pressure, I did encourage the German developer to flesh out a form of tagging, which did alleviate the problem to some extent. But as we see with Surf, they have pioneered in another direction. That brings us back to Nostr. Where can we look for the best solution? There simply isn't one yet. But, we can look at some other options for inspiration. HedgeDoc: https://hedgedoc.org/ I am eager for someone to fork HedgeDoc and employ Nostr sign-in. This is a small step toward managing information together within the Nostr ecosystem. I will attempt this myself eventually, if no one else does, but I am prioritizing my development in this way: 1. A nostr client that allows the cataloguing and management of relays locally. 2. A LogSeq alternative with Nostr interoperability. 3. HedgeDoc + Nostr is #3 on my list, despite being the easiest option. Check out HedgeDoc 2.0 if you have any interest in a cooperative Markdown experience on Nostr: https://docs.hedgedoc.dev/ Now, this article should catch up all of my dearest followers, and idols, to where I stand with "bookmarking, note-taking, list-making, kind-1 event management, frameworking, and so on..." Where it leads us to, is what's possible. Let's take a look at what's possible, once we forego ALL OF THE PROPRIETARY WEB'S BEST OPTIONS: https://denizaydemir.org/ https://denizaydemir.org/graph/how-logseq-should-build-a-world-knowledge-graph/ https://subconscious.network/ Nostr is even inspired by much of the history that has gone into information management systems. nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn I know looks up to Gordon Brander, just as I do. You can read his articles here: https://substack.com/@gordonbrander and they are very much worth reading! Also, I could note that the original version of Highlighter by nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft was also inspired partially by WorkFlowy. About a year ago, I was mesmerized coming across SubText and thinking I had finally found the answer Nostr might even be looking for. But, for now I will just suggest that others read the Readme.md on the SubText Gtihub, as well as articles by Brander. Good luck everyone. I am here to work with ANYONE who is interested in these type of solution on Nostr. My first order of business in this space is to spearhead a community of npubs who share this goal. Everyone who is interested in note-taking or list-making or bookmarking is welcome to join. I have created an INVITE-ONLY relay for this very purpose, and anyone is welcome to reach out if they wish to be added to the whitelist. It should be freely readable in the near future, if it is not already, but for now will remain a closed-to-post community to preemptively mitigate attack or spam. Please reach out to me if you wish to join the relay. https://logstr.mycelium.social/ With this article, I hope people will investigate and explore the options available. We have lots of ground to cover, but all of the right resources and manpower to do so. Godspeed, Nostr. #Nostr #Notes #OtherStuff #LogSec #Joplin #Obsidian
@ 50809a53:e091f164
2025-01-20 22:30:01For starters, anyone who is interested in curating and managing "notes, lists, bookmarks, kind-1 events, or other stuff" should watch this video: https://youtu.be/XRpHIa-2XCE Now, assuming you have watched it, I will proceed assuming you are aware of many of the applications that exist for a very similar purpose. I'll break them down further, following a similar trajectory in order of how I came across them, and a bit about my own path on this journey. We'll start way back in the early 2000s, before Bitcoin existed. We had https://zim-wiki.org/ It is tried and true, and to this day stands to present an option for people looking for a very simple solution to a potentially complex problem. Zim-Wiki works. But it is limited. Let's step into the realm of proprietary. Obsidian, Joplin, and LogSeq. The first two are entirely cloud-operative applications, with more of a focus on the true benefit of being a paid service. I will assume anyone reading this is capable of exploring the marketing of these applications, or trying their freemium product, to get a feeling for what they are capable of. I bring up Obsidian because it is very crucial to understand the market placement of publication. We know social media handles the 'hosting' problem of publishing notes "and other stuff" by harvesting data and making deals with advertisers. But- what Obsidian has evolved to offer is a full service known as 'publish'. This means users can stay in the proprietary pipeline, "from thought to web." all for $8/mo. See: https://obsidian.md/publish THIS IS NOSTR'S PRIMARY COMPETITION. WE ARE HERE TO DISRUPT THIS MARKET, WITH NOTES AND OTHER STUFF. WITH RELAYS. WITH THE PROTOCOL. Now, on to Joplin. I have never used this, because I opted to study the FOSS market and stayed free of any reliance on a paid solution. Many people like Joplin, and I gather the reason is because it has allowed itself to be flexible and good options that integrate with Joplin seems to provide good solutions for users who need that functionality. I see Nostr users recommending Joplin, so I felt it was worthwhile to mention as a case-study option. I myself need to investigate it more, but have found comfort in other solutions. LogSeq - This is my "other solutions." It seems to be trapped in its proprietary web of funding and constraint. I use it because it turns my desktop into a power-house of note archival. But by using it- I AM TRAPPED TOO. This means LogSeq is by no means a working solution for Nostr users who want a long-term archival option. But the trap is not a cage. It's merely a box. My notes can be exported to other applications with graphing and node-based information structure. Specifically, I can export these notes to: - Text - OPML - HTML - and, PNG, for whatever that is worth. Let's try out the PNG option, just for fun. Here's an exported PNG of my "Games on Nostr" list, which has long been abandoned. I once decided to poll some CornyChat users to see what games they enjoyed- and I documented them in a LogSeq page for my own future reference. You can see it here: https://i.postimg.cc/qMBPDTwr/image.png This is a very simple example of how a single "page" or "list" in LogSeq can be multipurpose. It is a small list, with multiple "features" or variables at play. First, I have listed out a variety of complex games that might make sense with "multiplayer" identification that relies on our npubs or nip-05 addresses to aggregate user data. We can ALL imagine playing games like Tetris, Snake, or Catan together with our Nostr identities. But of course we are a long way from breaking into the video game market. On a mostly irrelevant sidenote- you might notice in my example list, that I seem to be excited about a game called Dot.Hack. I discovered this small game on Itch.io and reached out to the developer on Twitter, in an attempt to purple-pill him, but moreso to inquire about his game. Unfortunately there was no response, even without mention of Nostr. Nonetheless, we pioneer on. You can try the game here: https://propuke.itch.io/planethack So instead let's focus on the structure of "one working list." The middle section of this list is where I polled users, and simply listed out their suggestions. Of course we discussed these before I documented, so it is note a direct result of a poll, but actually a working interaction of poll results! This is crucial because it separates my list from the aggregated data, and implies its relevance/importance. The final section of this ONE list- is the beginnings of where I conceptually connect nostr with video game functionality. You can look at this as the beginning of a new graph, which would be "Video Game Operability With Nostr". These three sections make up one concept within my brain. It exists in other users' brains too- but of course they are not as committed to the concept as myself- the one managing the communal discussion. With LogSeq- I can grow and expand these lists. These lists can become graphs. Those graphs can become entire catalogues of information than can be shared across the web. I can replicate this system with bookmarks, ideas, application design, shopping lists, LLM prompting, video/music playlists, friend lists, RELAY lists, the LIST goes ON forever! So where does that lead us? I think it leads us to kind-1 events. We don't have much in the way of "kind-1 event managers" because most developers would agree that "storing kind-1 events locally" is.. at the very least, not so important. But it could be! If only a superapp existed that could interface seamlessly with nostr, yada yada.. we've heard it all before. We aren't getting a superapp before we have microapps. Basically this means frameworking the protocol before worrying about the all-in-one solution. So this article will step away from the deep desire for a Nostr-enabled, Rust-built, FOSS, non-commercialized FREEDOM APP, that will exist one day, we hope. Instead, we will focus on simple attempts of the past. I encourage others to chime in with their experience. Zim-Wiki is foundational. The user constructs pages, and can then develop them into books. LogSeq has the right idea- but is constrained in too many ways to prove to be a working solution at this time. However, it is very much worth experimenting with, and investigating, and modelling ourselves after. https://workflowy.com/ is next on our list. This is great for users who think LogSeq is too complex. They "just want simple notes." Get a taste with WorkFlowy. You will understand why LogSeq is powerful if you see value in WF. I am writing this article in favor of a redesign of LogSeq to be compatible with Nostr. I have been drafting the idea since before Nostr existed- and with Nostr I truly believe it will be possible. So, I will stop to thank everyone who has made Nostr what it is today. I wouldn't be publishing this without you! One app I need to investigate more is Zettlr. I will mention it here for others to either discuss or investigate, as it is also mentioned some in the video I opened with. https://www.zettlr.com/ On my path to finding Nostr, before its inception, was a service called Deta.Space. This was an interesting project, not entirely unique or original, but completely fresh and very beginner-friendly. DETA WAS AN AWESOME CLOUD OS. And we could still design a form of Nostr ecosystem that is managed in this way. But, what we have now is excellent, and going forward I only see "additional" or supplemental. Along the timeline, Deta sunsetted their Space service and launched https://deta.surf/ You might notice they advertise that "This is the future of bookmarks." I have to wonder if perhaps I got through to them that bookmarking was what their ecosystem could empower. While I have not tried Surf, it looks interested, but does not seem to address what I found most valuable about Deta.Space: https://webcrate.app/ WebCrate was an early bookmarking client for Deta.Space which was likely their most popular application. What was amazing about WebCrate was that it delivered "simple bookmarking." At one point I decided to migrate my bookmarks from other apps, like Pocket and WorkFlowy, into WebCrate. This ended up being an awful decision, because WebCrate is no longer being developed. However, to much credit of Deta.Space, my WebCrate instance is still running and completely functional. I have since migrated what I deem important into a local LogSeq graph, so my bookmarks are safe. But, the development of WebCrate is note. WebCrate did not provide a working directory of crates. All creates were contained within a single-level directory. Essentially there were no layers. Just collections of links. This isn't enough for any user to effectively manage their catalogue of notes. With some pressure, I did encourage the German developer to flesh out a form of tagging, which did alleviate the problem to some extent. But as we see with Surf, they have pioneered in another direction. That brings us back to Nostr. Where can we look for the best solution? There simply isn't one yet. But, we can look at some other options for inspiration. HedgeDoc: https://hedgedoc.org/ I am eager for someone to fork HedgeDoc and employ Nostr sign-in. This is a small step toward managing information together within the Nostr ecosystem. I will attempt this myself eventually, if no one else does, but I am prioritizing my development in this way: 1. A nostr client that allows the cataloguing and management of relays locally. 2. A LogSeq alternative with Nostr interoperability. 3. HedgeDoc + Nostr is #3 on my list, despite being the easiest option. Check out HedgeDoc 2.0 if you have any interest in a cooperative Markdown experience on Nostr: https://docs.hedgedoc.dev/ Now, this article should catch up all of my dearest followers, and idols, to where I stand with "bookmarking, note-taking, list-making, kind-1 event management, frameworking, and so on..." Where it leads us to, is what's possible. Let's take a look at what's possible, once we forego ALL OF THE PROPRIETARY WEB'S BEST OPTIONS: https://denizaydemir.org/ https://denizaydemir.org/graph/how-logseq-should-build-a-world-knowledge-graph/ https://subconscious.network/ Nostr is even inspired by much of the history that has gone into information management systems. nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn I know looks up to Gordon Brander, just as I do. You can read his articles here: https://substack.com/@gordonbrander and they are very much worth reading! Also, I could note that the original version of Highlighter by nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft was also inspired partially by WorkFlowy. About a year ago, I was mesmerized coming across SubText and thinking I had finally found the answer Nostr might even be looking for. But, for now I will just suggest that others read the Readme.md on the SubText Gtihub, as well as articles by Brander. Good luck everyone. I am here to work with ANYONE who is interested in these type of solution on Nostr. My first order of business in this space is to spearhead a community of npubs who share this goal. Everyone who is interested in note-taking or list-making or bookmarking is welcome to join. I have created an INVITE-ONLY relay for this very purpose, and anyone is welcome to reach out if they wish to be added to the whitelist. It should be freely readable in the near future, if it is not already, but for now will remain a closed-to-post community to preemptively mitigate attack or spam. Please reach out to me if you wish to join the relay. https://logstr.mycelium.social/ With this article, I hope people will investigate and explore the options available. We have lots of ground to cover, but all of the right resources and manpower to do so. Godspeed, Nostr. #Nostr #Notes #OtherStuff #LogSec #Joplin #Obsidian @ cff1720e:15c7e2b2
2025-01-19 17:48:02**Einleitung**\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie <roland@pareto.space> können sie sogar jederzeit umziehen, egal wohin. **Cool, das ist state of the art!** Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.  **Warum Nostr?** Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz **"unserer Demokratie”** praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.  Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ **Resümee:** keine Standards, keine Daten, keine Rechte = keine Zukunft!  \ **Wie funktioniert Nostr?** Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum **“single point of failure”**, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. <roland@pareto.space> ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ **Resümee:** ein offener Standard, alle Daten, alle Rechte = große Zukunft!  \ **Warum ist Nostr die Zukunft des Internet?** “Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie **(Value4Value)**. OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.  \ **Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.** <https://nostr.net/> \ <https://start.njump.me/> **Hier das Interview zum Thema mit Radio Berliner Morgenröte** <https://www.podbean.com/ew/pb-yxc36-17bb4be>
@ cff1720e:15c7e2b2
2025-01-19 17:48:02**Einleitung**\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie <roland@pareto.space> können sie sogar jederzeit umziehen, egal wohin. **Cool, das ist state of the art!** Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.  **Warum Nostr?** Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz **"unserer Demokratie”** praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.  Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ **Resümee:** keine Standards, keine Daten, keine Rechte = keine Zukunft!  \ **Wie funktioniert Nostr?** Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum **“single point of failure”**, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. <roland@pareto.space> ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ **Resümee:** ein offener Standard, alle Daten, alle Rechte = große Zukunft!  \ **Warum ist Nostr die Zukunft des Internet?** “Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie **(Value4Value)**. OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.  \ **Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.** <https://nostr.net/> \ <https://start.njump.me/> **Hier das Interview zum Thema mit Radio Berliner Morgenröte** <https://www.podbean.com/ew/pb-yxc36-17bb4be> @ ac6f9572:8a6853dd
2025-02-13 01:55:20# Freedom Tech, Privacy, Sound Money, and Culture: How to Find Your Tribe? > Keeping up with everything happening in Bitcoin isn’t easy, even if you’ve been around for a while. The pace is relentless: stream of events, discussions, projects, and updates, not to mention the noise on social media...  Date: 02/12/2025 One of the most efficient options to expand your knowledge and truly connect with people actively working in the space is through direct interactions, whether they’re happening at large conferences or smaller, semi-official meetups. But let’s be honest: finding all meaningful events can be a mess. Take, for example, the '[BTC Events Map](https://docs.google.com/spreadsheets/d/1oni0QAHb2XYOL5gFVKHHGhG8w_HY5GDGBhdQ4SSrCZg/edit?gid=0&ref=europeanbitcoiners.com#gid=0),’ which already lists over 550 Bitcoin-only gatherings worldwide. This simple but very useful resource, put together by Satlantis, can help many of us plan our trips throughout the year. However, if you don’t know about its existence and rely solely on a search engine—whether Google or Brave—you’ll likely end up frustrated (and unfortunately missing many great opportunities to meet with others and learn). Search for '_bitcoin events_,' and you’ll get a mix of irrelevant crypto, fintech, and Web3 results, with Bitcoin-related stuff buried somewhere in the middle, if at all.. Well, it’s really tough to find what you’re actually looking for. That’s why word of mouth and trusted communities are so important. Sometimes, the best way to hear about an event is directly from people you know. **One of those that flew under my radar was** [**SatsNFacts**](https://satsnfacts.btc.pub/?ref=europeanbitcoiners.com)**.** It wasn’t listed on many typical event aggregators or any big news-promo sites. It mostly spread peer-to-peer and through the main channels on [Nostr](https://njump.me/npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx?ref=europeanbitcoiners.com). I was ‘_lucky_’ enough to hear about it just in time to plan the trip from Europe to Thailand. Now, I’d like to briefly share my experience with you—everything that, in my opinion, made this event truly stand out. **A Journey to Southeast Asia: Where Builders and Artists Collide.** -------------------------------------------------------------------- Approximately 10,176 kilometers, 14 hours of travel, and finally three days spent at SatsNFacts—"Thailand’s first Bitcoin Technical Unconference”. The event ran from February 8 to 10 in Chiang Mai (the largest city in northern Thailand). Held at Weave Artisan Society, a 700 sq.m venue that used to be an ice factory, it smoothly combined pleasant outdoors with an industrial-style, two-floor indoor area, creating a unique and very practical setup. While its was billed as a “_Technical Unconference_,” in practice it nicely connected the developer-based ecosystem with different aspects of culture and art. Each day, from 10 am to 6 pm, the agenda—shaped directly by attendees—was packed with various presentations, group chats, learning session, hackathons, and actionable workshops. With many options available (around 10-20 topics per day), I couldn’t attend everything, but here are a few more technical sessions I joined and found especially worthwhile: * **Liana Workshop** (long-term security, recovery, and inheritance), * **TollGates** ([streaming sats for internet access](https://primal.net/e/naddr1qvzqqqr4gupzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68qq2nz63h0969vn2xwse9j3n5ge4xsdr2ddc4j0g960h?ref=europeanbitcoiners.com)), * **Open Vault** (enterprise wallet interface), * **Yaki Honne** ([decentralized media](https://yakihonne.com/?ref=europeanbitcoiners.com)), * **Nostr Proxies** (Epoxy, WebSocket and relay monetization). * **Silent payments** (simplified payment experiences without compromising privacy). As mentioned earlier, SatsNFacts wasn’t just about Bitcoin tech. Some topics focused on community aspects as well. Two discussions I joined highlighted Bitcoin adoption ⚡ in for example Bali and Thailand, showing how sound money, integrity, and consistent work can solve real problems in these regions. Impressive stuff! Here you can learn more: * [HuaiPhueng](https://geyser.fund/project/huaiphuengproject?hero=geyser&ref=europeanbitcoiners.com) on Geyser + "Bitcoin City" (their [short video](https://www.youtube.com/watch?feature=shared&v=211meP4liIo&ref=europeanbitcoiners.com)). * Bitcoin Indonesia & Bitcoin House Bali ([all in one on GitHub](https://github.com/bitcoinindo21?ref=europeanbitcoiners.com)) Now, the art gallery, to continue with less technical aspects of SatsNFacts 🎨 This nicely-organized space located on the ground floor, near cozy coworking and networking spots, was for me a real gem. Indeed, adding a creative vibe to the entire event. Around 30 unique works from local and international artists were on display, all inspired by themes of freedom and privacy. Though I don’t see myself as a typical _'artist_', I was honored to have some of my own pieces exhibited there as well (a short video below). * * * One of the highlights was meeting local Thai artists, especially [Siritravelsketch](https://njump.me/npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu?ref=europeanbitcoiners.com), who travelled six hours by train just one way to attend two days of the event. Her stunning paintings, created using just a bamboo stick and ink, are deeply inspired by Thai architecture and culture. While some of her pre-prepared pieces hung in the gallery, she also painted a few new works on the spot during her visit. Truly spectacular!  * * * I also had the chance to reconnect with [Satoshi Builds](https://njump.me/npub19m7m3rs66pfdn4ewhrm8slh60ukyxgrylaa03m73wa40j39lc03syq4gfu?ref=europeanbitcoiners.com), who made many great sketches during this event, and with [BitPopArt](https://njump.me/npub1gwa27rpgum8mr9d30msg8cv7kwj2lhav2nvmdwh3wqnsa5vnudxqlta2sz?ref=europeanbitcoiners.com), a Dutch artist who, just like me, chosen a nomadic lifestyle yet has been clearly considering Thailand his 'second home' as well for several years now. By the way, ✍️ here's his short summary of the event, focusing more on the artistic side of SatsNFacts: "[Art exhibition in Chiang Mai](https://bitpopart.com/2025/02/11/art-exhibition-in-chiang-mai/?ref=europeanbitcoiners.com)". All in all, spending my time in many meaningful conversations and seeing so many deep artworks in one place filled me with hope and positive energy. THANK YOU, EVERYONE!  * * * (presented artworks by for example: [Agi Choote](https://njump.me/npub1tlacuxmtv2wqud9qz0ujnr4mqavmnz3ayspfj93jr40tgf2mvu6seax3y7?ref=europeanbitcoiners.com), [Samhain](https://njump.me/npub1df47g7a39usamq83aula72zdz23fx9xw5rrfmd0v6p9t20n5u0ss2eqez9?ref=europeanbitcoiners.com), [Zed Erwan](https://njump.me/npub1r2sah0htqnw7xrs70gq00m48vp25neu8ym2n2ghrny92dqqf7sest8hth0?ref=europeanbitcoiners.com), [Existing Sprinkles](https://njump.me/npub1f5kc2agn63ecv2ua4909z9ahgmr2x9263na36jh6r908ql0926jq3nvk2u?ref=europeanbitcoiners.com), AZA 21m, BitPopArt.) * * * Mr. Rabbit in Thailand... ------------------------- Monday, the final evening, and SatsNFacts got one more item on its agenda rooted in creative expression and independent art. Representing [Bitcoin FilmFest](https://x.com/bitcoinfilmfest?ref=europeanbitcoiners.com) (a grassroots project created by an amazing group of freedom fighters and activists 🐇🧡), since I was the only one from our team in Thailand, in one of the rooms upstairs, I put together a mini cinematic experience. Seven trailers and eleven shorts, including for example: * NO MORE INFLATION, HUMMINGBIRD, PARALLEL SPACE, UNBANKABLE, THE LEGEND OF LANDI (🎬 some of the trailers). * BITCOIN A NEW HOPE, SATOSHI NAKAMOTO - THE CREATOR OF BITCOIN, MAXIS CLUB SHOW - CHAPTER ONE, THE GREATEST HEIST IN HISTORY, HODL, THE ANATOMY OF BITCOIN – GENESIS BLOCK (📺 some of the presented shorts) With around 10-15 participants, the response was positive, and we ended up spending an extra 10-maybe-20 minutes discussing the challenges and opportunities in Bitcoin-powered filmmaking, as well as the upcoming edition of [BFF25](https://bitcoinfilmfest.com/bff25/?ref=europeanbitcoiners.com) (the annual festival we're organizing this May in Warsaw, Poland).  **Substance Over Hype. Gatherings That Matter.** ------------------------------------------------ SatsNFacts made a solid reminder that Bitcoin events can help build a truly sovereign future while bringing together developers and artistic souls alike. The mix of technical depth and creative energy—free from the shiny gossip that floods many social channels—made it a truly meaningful experience. > SatsNFacts set a high standard, and I hope to see more events like it in the future. More unconferences, more cultural and community-driven gatherings. **Here's to more signal, less noise!!!** Big congrats to everyone who made the first SatsNFacts happen 👏 Respect especially to the organizers! You pulled off something truly special! * * * _BTC Your Mind. Let it Beat._ _Şela_ @AZA_21M 💡 Did you enjoy this article? Zap me some sats. No amount is small :) Lightning wallet: `aza21m@getalby.com` - - - Original Article: https://europeanbitcoiners.com/sats-and-facts-short-coverage-of-the-first-bitcoin-unconference-in-thailand/ #english #opinion #events #bitcoin #nostr #freedom #conference #siamstr #asia #thailand originally posted at https://stacker.news/items/884317
@ ac6f9572:8a6853dd
2025-02-13 01:55:20# Freedom Tech, Privacy, Sound Money, and Culture: How to Find Your Tribe? > Keeping up with everything happening in Bitcoin isn’t easy, even if you’ve been around for a while. The pace is relentless: stream of events, discussions, projects, and updates, not to mention the noise on social media...  Date: 02/12/2025 One of the most efficient options to expand your knowledge and truly connect with people actively working in the space is through direct interactions, whether they’re happening at large conferences or smaller, semi-official meetups. But let’s be honest: finding all meaningful events can be a mess. Take, for example, the '[BTC Events Map](https://docs.google.com/spreadsheets/d/1oni0QAHb2XYOL5gFVKHHGhG8w_HY5GDGBhdQ4SSrCZg/edit?gid=0&ref=europeanbitcoiners.com#gid=0),’ which already lists over 550 Bitcoin-only gatherings worldwide. This simple but very useful resource, put together by Satlantis, can help many of us plan our trips throughout the year. However, if you don’t know about its existence and rely solely on a search engine—whether Google or Brave—you’ll likely end up frustrated (and unfortunately missing many great opportunities to meet with others and learn). Search for '_bitcoin events_,' and you’ll get a mix of irrelevant crypto, fintech, and Web3 results, with Bitcoin-related stuff buried somewhere in the middle, if at all.. Well, it’s really tough to find what you’re actually looking for. That’s why word of mouth and trusted communities are so important. Sometimes, the best way to hear about an event is directly from people you know. **One of those that flew under my radar was** [**SatsNFacts**](https://satsnfacts.btc.pub/?ref=europeanbitcoiners.com)**.** It wasn’t listed on many typical event aggregators or any big news-promo sites. It mostly spread peer-to-peer and through the main channels on [Nostr](https://njump.me/npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx?ref=europeanbitcoiners.com). I was ‘_lucky_’ enough to hear about it just in time to plan the trip from Europe to Thailand. Now, I’d like to briefly share my experience with you—everything that, in my opinion, made this event truly stand out. **A Journey to Southeast Asia: Where Builders and Artists Collide.** -------------------------------------------------------------------- Approximately 10,176 kilometers, 14 hours of travel, and finally three days spent at SatsNFacts—"Thailand’s first Bitcoin Technical Unconference”. The event ran from February 8 to 10 in Chiang Mai (the largest city in northern Thailand). Held at Weave Artisan Society, a 700 sq.m venue that used to be an ice factory, it smoothly combined pleasant outdoors with an industrial-style, two-floor indoor area, creating a unique and very practical setup. While its was billed as a “_Technical Unconference_,” in practice it nicely connected the developer-based ecosystem with different aspects of culture and art. Each day, from 10 am to 6 pm, the agenda—shaped directly by attendees—was packed with various presentations, group chats, learning session, hackathons, and actionable workshops. With many options available (around 10-20 topics per day), I couldn’t attend everything, but here are a few more technical sessions I joined and found especially worthwhile: * **Liana Workshop** (long-term security, recovery, and inheritance), * **TollGates** ([streaming sats for internet access](https://primal.net/e/naddr1qvzqqqr4gupzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68qq2nz63h0969vn2xwse9j3n5ge4xsdr2ddc4j0g960h?ref=europeanbitcoiners.com)), * **Open Vault** (enterprise wallet interface), * **Yaki Honne** ([decentralized media](https://yakihonne.com/?ref=europeanbitcoiners.com)), * **Nostr Proxies** (Epoxy, WebSocket and relay monetization). * **Silent payments** (simplified payment experiences without compromising privacy). As mentioned earlier, SatsNFacts wasn’t just about Bitcoin tech. Some topics focused on community aspects as well. Two discussions I joined highlighted Bitcoin adoption ⚡ in for example Bali and Thailand, showing how sound money, integrity, and consistent work can solve real problems in these regions. Impressive stuff! Here you can learn more: * [HuaiPhueng](https://geyser.fund/project/huaiphuengproject?hero=geyser&ref=europeanbitcoiners.com) on Geyser + "Bitcoin City" (their [short video](https://www.youtube.com/watch?feature=shared&v=211meP4liIo&ref=europeanbitcoiners.com)). * Bitcoin Indonesia & Bitcoin House Bali ([all in one on GitHub](https://github.com/bitcoinindo21?ref=europeanbitcoiners.com)) Now, the art gallery, to continue with less technical aspects of SatsNFacts 🎨 This nicely-organized space located on the ground floor, near cozy coworking and networking spots, was for me a real gem. Indeed, adding a creative vibe to the entire event. Around 30 unique works from local and international artists were on display, all inspired by themes of freedom and privacy. Though I don’t see myself as a typical _'artist_', I was honored to have some of my own pieces exhibited there as well (a short video below). * * * One of the highlights was meeting local Thai artists, especially [Siritravelsketch](https://njump.me/npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu?ref=europeanbitcoiners.com), who travelled six hours by train just one way to attend two days of the event. Her stunning paintings, created using just a bamboo stick and ink, are deeply inspired by Thai architecture and culture. While some of her pre-prepared pieces hung in the gallery, she also painted a few new works on the spot during her visit. Truly spectacular!  * * * I also had the chance to reconnect with [Satoshi Builds](https://njump.me/npub19m7m3rs66pfdn4ewhrm8slh60ukyxgrylaa03m73wa40j39lc03syq4gfu?ref=europeanbitcoiners.com), who made many great sketches during this event, and with [BitPopArt](https://njump.me/npub1gwa27rpgum8mr9d30msg8cv7kwj2lhav2nvmdwh3wqnsa5vnudxqlta2sz?ref=europeanbitcoiners.com), a Dutch artist who, just like me, chosen a nomadic lifestyle yet has been clearly considering Thailand his 'second home' as well for several years now. By the way, ✍️ here's his short summary of the event, focusing more on the artistic side of SatsNFacts: "[Art exhibition in Chiang Mai](https://bitpopart.com/2025/02/11/art-exhibition-in-chiang-mai/?ref=europeanbitcoiners.com)". All in all, spending my time in many meaningful conversations and seeing so many deep artworks in one place filled me with hope and positive energy. THANK YOU, EVERYONE!  * * * (presented artworks by for example: [Agi Choote](https://njump.me/npub1tlacuxmtv2wqud9qz0ujnr4mqavmnz3ayspfj93jr40tgf2mvu6seax3y7?ref=europeanbitcoiners.com), [Samhain](https://njump.me/npub1df47g7a39usamq83aula72zdz23fx9xw5rrfmd0v6p9t20n5u0ss2eqez9?ref=europeanbitcoiners.com), [Zed Erwan](https://njump.me/npub1r2sah0htqnw7xrs70gq00m48vp25neu8ym2n2ghrny92dqqf7sest8hth0?ref=europeanbitcoiners.com), [Existing Sprinkles](https://njump.me/npub1f5kc2agn63ecv2ua4909z9ahgmr2x9263na36jh6r908ql0926jq3nvk2u?ref=europeanbitcoiners.com), AZA 21m, BitPopArt.) * * * Mr. Rabbit in Thailand... ------------------------- Monday, the final evening, and SatsNFacts got one more item on its agenda rooted in creative expression and independent art. Representing [Bitcoin FilmFest](https://x.com/bitcoinfilmfest?ref=europeanbitcoiners.com) (a grassroots project created by an amazing group of freedom fighters and activists 🐇🧡), since I was the only one from our team in Thailand, in one of the rooms upstairs, I put together a mini cinematic experience. Seven trailers and eleven shorts, including for example: * NO MORE INFLATION, HUMMINGBIRD, PARALLEL SPACE, UNBANKABLE, THE LEGEND OF LANDI (🎬 some of the trailers). * BITCOIN A NEW HOPE, SATOSHI NAKAMOTO - THE CREATOR OF BITCOIN, MAXIS CLUB SHOW - CHAPTER ONE, THE GREATEST HEIST IN HISTORY, HODL, THE ANATOMY OF BITCOIN – GENESIS BLOCK (📺 some of the presented shorts) With around 10-15 participants, the response was positive, and we ended up spending an extra 10-maybe-20 minutes discussing the challenges and opportunities in Bitcoin-powered filmmaking, as well as the upcoming edition of [BFF25](https://bitcoinfilmfest.com/bff25/?ref=europeanbitcoiners.com) (the annual festival we're organizing this May in Warsaw, Poland).  **Substance Over Hype. Gatherings That Matter.** ------------------------------------------------ SatsNFacts made a solid reminder that Bitcoin events can help build a truly sovereign future while bringing together developers and artistic souls alike. The mix of technical depth and creative energy—free from the shiny gossip that floods many social channels—made it a truly meaningful experience. > SatsNFacts set a high standard, and I hope to see more events like it in the future. More unconferences, more cultural and community-driven gatherings. **Here's to more signal, less noise!!!** Big congrats to everyone who made the first SatsNFacts happen 👏 Respect especially to the organizers! You pulled off something truly special! * * * _BTC Your Mind. Let it Beat._ _Şela_ @AZA_21M 💡 Did you enjoy this article? Zap me some sats. No amount is small :) Lightning wallet: `aza21m@getalby.com` - - - Original Article: https://europeanbitcoiners.com/sats-and-facts-short-coverage-of-the-first-bitcoin-unconference-in-thailand/ #english #opinion #events #bitcoin #nostr #freedom #conference #siamstr #asia #thailand originally posted at https://stacker.news/items/884317 @ fd208ee8:0fd927c1
2025-01-19 12:10:10I am so tired of people trying to waste my time with Nostrized imitations of stuff that already exists. Instagram, but make it Nostr. Twitter, but make it Nostr. GitHub, but make it Nostr. Facebook, but make it Nostr. Wordpress, but make it Nostr. GoodReads, but make it Nostr. TikTok, but make it Nostr. That stuff already exists, and it wasn't that great the first time around, either. Build something better than that stuff, that can only be brought into existence because of Nostr. Build something that does something completely and awesomely new. Knock my socks off, bro. Cuz, ain't nobody got time for that.
@ fd208ee8:0fd927c1
2025-01-19 12:10:10I am so tired of people trying to waste my time with Nostrized imitations of stuff that already exists. Instagram, but make it Nostr. Twitter, but make it Nostr. GitHub, but make it Nostr. Facebook, but make it Nostr. Wordpress, but make it Nostr. GoodReads, but make it Nostr. TikTok, but make it Nostr. That stuff already exists, and it wasn't that great the first time around, either. Build something better than that stuff, that can only be brought into existence because of Nostr. Build something that does something completely and awesomely new. Knock my socks off, bro. Cuz, ain't nobody got time for that. @ 1cb14ab3:95d52462
2025-02-13 01:30:00**Dirt, body weight. [125' x 2']** *This project was exhibited in 2015 in Boulder, Colorado.* --- ### Artist Statement “A Line Made By Walking” (2015) is a site-specific piece created in Boulder, CO, where my body weight etched a temporary line into the earth. This work pays homage to Richard Long’s seminal 1967 piece, where a simple act of walking through the landscape left a profound trace. In my version, the line created by my movement forces the viewer to engage with the impermanence of human intervention on the land. The project prompts a reflection on the subtle yet lasting impacts we have on the environment, even through seemingly minimal actions. As part of my larger “[Rockway](https://hes.npub.pro/post/1708400183541/)” project, this case study explores the concept of ‘line’ in both literal and metaphorical ways. The line is not just a physical mark, but also a representation of time, movement, and the dialogue between the body and the land. Walking, in this context, becomes a way of marking time—an act that is as ephemeral as the mark it leaves behind. The work questions the tension between permanence and transience, asking the viewer to consider how we interact with the land, both intentionally and unknowingly, and how those interactions leave traces that may soon fade but never completely disappear. --- ### Photos        --- #### More Land Art: [Earth Lens Series](https://hes.npub.pro/post/1731091744332/) ["Looking Glass"](https://hes.npub.pro/post/1736304563962/) ["Het Bonhe"](https://hes.npub.pro/post/1720242458557/) ["Rockway"](https://hes.npub.pro/post/1708400183541/) ["Invasive"](https://hes.npub.pro/post/1719722211094/) --- #### More from Hes [Full Portfolio](https://hesart.npub.pro) [Online Store](https://plebeian.market/community/hes@nostrplebs.com/hesmart-ym3fcufdfz) [Artist Statements](https://hes.npub.pro/tag/art/) [Travel Guides](https://hes.npub.pro/tag/travel/) [Photography](https://hes.npub.pro/tag/photography) [Writings](https://hes.npub.pro/tag/money) --- *All images are credit of Hes, but you are free to download and use for any purpose. If you find joy from my art, please feel free to send a zap. Enjoy life on a Bitcoin standard.*
@ 1cb14ab3:95d52462
2025-02-13 01:30:00**Dirt, body weight. [125' x 2']** *This project was exhibited in 2015 in Boulder, Colorado.* --- ### Artist Statement “A Line Made By Walking” (2015) is a site-specific piece created in Boulder, CO, where my body weight etched a temporary line into the earth. This work pays homage to Richard Long’s seminal 1967 piece, where a simple act of walking through the landscape left a profound trace. In my version, the line created by my movement forces the viewer to engage with the impermanence of human intervention on the land. The project prompts a reflection on the subtle yet lasting impacts we have on the environment, even through seemingly minimal actions. As part of my larger “[Rockway](https://hes.npub.pro/post/1708400183541/)” project, this case study explores the concept of ‘line’ in both literal and metaphorical ways. The line is not just a physical mark, but also a representation of time, movement, and the dialogue between the body and the land. Walking, in this context, becomes a way of marking time—an act that is as ephemeral as the mark it leaves behind. The work questions the tension between permanence and transience, asking the viewer to consider how we interact with the land, both intentionally and unknowingly, and how those interactions leave traces that may soon fade but never completely disappear. --- ### Photos        --- #### More Land Art: [Earth Lens Series](https://hes.npub.pro/post/1731091744332/) ["Looking Glass"](https://hes.npub.pro/post/1736304563962/) ["Het Bonhe"](https://hes.npub.pro/post/1720242458557/) ["Rockway"](https://hes.npub.pro/post/1708400183541/) ["Invasive"](https://hes.npub.pro/post/1719722211094/) --- #### More from Hes [Full Portfolio](https://hesart.npub.pro) [Online Store](https://plebeian.market/community/hes@nostrplebs.com/hesmart-ym3fcufdfz) [Artist Statements](https://hes.npub.pro/tag/art/) [Travel Guides](https://hes.npub.pro/tag/travel/) [Photography](https://hes.npub.pro/tag/photography) [Writings](https://hes.npub.pro/tag/money) --- *All images are credit of Hes, but you are free to download and use for any purpose. If you find joy from my art, please feel free to send a zap. Enjoy life on a Bitcoin standard.* @ 20e7c953:3b8bcb21
2025-02-13 01:15:42Biggest takeaway? We needed more hands to cover key roles - something to improve for next time, if there is any! That said, the strongest point was the organic networking and building, which set this apart from more structured, commercial conferences. For future events - if any! - Hackathons will need dedicated time slots in the future, given the time constraints. The art side of things isn’t over yet—the exhibition will keep going for another month. The event started a bit messy, but the quality of people made it flow naturally, creating a unique and engaging atmosphere. Overall, a great experience, and we’ll keep iterating for the next one. We’ll send out a survey soon to gather more feedback. Huge thanks to our sponsors and media partners for making this happen - appreciate the support. On Communities: Lastly, while both commercial and less commercial events are needed there is something that doesn't beat Bitcoin Culture which are Bitcoin-only Meetups. If we are in a position to give some advice: Make sure you engage with your local community since people behind it are most likely the ones who can able to bootstrap new comers while keeping trust and accountability in place. Luckily today we have most tools to filter out those who are leeching off others PoW and the genuine ones trailblazing on their own terms. On our side definitely one of the biggest lessons learnt was to work with the local Communities for future events - regardless - this time we managed to get it done with our hands, will and not much else since *most* tools used have been FOSS and that's why we are here for ! With that said and while continuously gathering more feedback these coming days.... WHAT DID YOU ENJOYED THE MOST? ANYTHING YOU DISLIKED? **WHERE SHOULD WE HOST SATS N FACTS NEXT ?👀** SUGGESTIONS AND FEEDBACK MAILBOX IS OPEN 📬 Onwards 🫡
@ 20e7c953:3b8bcb21
2025-02-13 01:15:42Biggest takeaway? We needed more hands to cover key roles - something to improve for next time, if there is any! That said, the strongest point was the organic networking and building, which set this apart from more structured, commercial conferences. For future events - if any! - Hackathons will need dedicated time slots in the future, given the time constraints. The art side of things isn’t over yet—the exhibition will keep going for another month. The event started a bit messy, but the quality of people made it flow naturally, creating a unique and engaging atmosphere. Overall, a great experience, and we’ll keep iterating for the next one. We’ll send out a survey soon to gather more feedback. Huge thanks to our sponsors and media partners for making this happen - appreciate the support. On Communities: Lastly, while both commercial and less commercial events are needed there is something that doesn't beat Bitcoin Culture which are Bitcoin-only Meetups. If we are in a position to give some advice: Make sure you engage with your local community since people behind it are most likely the ones who can able to bootstrap new comers while keeping trust and accountability in place. Luckily today we have most tools to filter out those who are leeching off others PoW and the genuine ones trailblazing on their own terms. On our side definitely one of the biggest lessons learnt was to work with the local Communities for future events - regardless - this time we managed to get it done with our hands, will and not much else since *most* tools used have been FOSS and that's why we are here for ! With that said and while continuously gathering more feedback these coming days.... WHAT DID YOU ENJOYED THE MOST? ANYTHING YOU DISLIKED? **WHERE SHOULD WE HOST SATS N FACTS NEXT ?👀** SUGGESTIONS AND FEEDBACK MAILBOX IS OPEN 📬 Onwards 🫡 @ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |  | **Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2,** | | Pen drive |  | **16Gb** | Recomendo que use o **Ubuntu Server** para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi [aqui]( https://ubuntu.com/download/raspberry-pi). O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível [aqui]( https://ubuntu.com/tutorials/how-to-install-ubuntu-on-your-raspberry-pi). **Não instale um desktop** (como xubuntu, lubuntu, xfce, etc.). --- ## Passo 1: Atualizar o Sistema 🖥️ Primeiro, atualize seu sistema e instale o Tor: ```bash apt update apt install tor ``` --- ## Passo 2: Criar o Arquivo de Serviço `nrs.service` 🔧 Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo: ```unit [Unit] Description=Nostr Relay Server Service After=network.target [Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure [Install] WantedBy=multi-user.target ``` --- ## Passo 3: Baixar o Binário do Nostr 🚀 Baixe o binário mais recente do Nostr [aqui no GitHub]( https://github.com/gabrielmoura/SimpleNosrtRelay/releases). --- ## Passo 4: Criar as Pastas Necessárias 📂 Agora, crie as pastas para o aplicativo e o pendrive: ```bash mkdir -p /opt/nrs /mnt/edriver ``` --- ## Passo 5: Listar os Dispositivos Conectados 🔌 Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados: ```bash lsblk ``` --- ## Passo 6: Formatando o Pendrive 💾 Escolha o pendrive correto (por exemplo, `/dev/sda`) e formate-o: ```bash mkfs.vfat /dev/sda ``` --- ## Passo 7: Montar o Pendrive 💻 Monte o pendrive na pasta `/mnt/edriver`: ```bash mount /dev/sda /mnt/edriver ``` --- ## Passo 8: Verificar UUID dos Dispositivos 📋 Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados: ```bash blkid ``` --- ## Passo 9: Alterar o `fstab` para Montar o Pendrive Automáticamente 📝 Abra o arquivo `/etc/fstab` e adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim: ```fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0 ``` --- ## Passo 10: Copiar o Binário para a Pasta Correta 📥 Agora, copie o binário baixado para a pasta `/opt/nrs`: ```bash cp nrs-arm64 /opt/nrs ``` --- ## Passo 11: Criar o Arquivo de Configuração 🛠️ Crie o arquivo de configuração com o seguinte conteúdo e salve-o em `/opt/nrs/config.yaml`: ```yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true ``` --- ## Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️ Agora, copie o arquivo `nrs.service` para o diretório `/etc/systemd/system/`: ```bash cp nrs.service /etc/systemd/system/ ``` Recarregue os serviços e inicie o serviço `nrs`: ```bash systemctl daemon-reload systemctl enable --now nrs.service ``` --- ## Passo 13: Configurar o Tor 🌐 Abra o arquivo de configuração do Tor `/var/lib/tor/torrc` e adicione a seguinte linha: ```torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334 ``` --- ## Passo 14: Habilitar e Iniciar o Tor 🧅 Agora, ative e inicie o serviço Tor: ```bash systemctl enable --now tor.service ``` O Tor irá gerar um endereço `.onion` para o seu servidor Nostr. Você pode encontrá-lo no arquivo `/var/lib/tor/nostr_server/hostname`. --- ## Observações ⚠️ - Com essa configuração, **os dados serão salvos no pendrive**, enquanto o binário ficará no cartão SD do Raspberry Pi. - O endereço `.onion` do seu servidor Nostr será algo como: `ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion`. --- Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳 Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |  | **Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2,** | | Pen drive |  | **16Gb** | Recomendo que use o **Ubuntu Server** para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi [aqui]( https://ubuntu.com/download/raspberry-pi). O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível [aqui]( https://ubuntu.com/tutorials/how-to-install-ubuntu-on-your-raspberry-pi). **Não instale um desktop** (como xubuntu, lubuntu, xfce, etc.). --- ## Passo 1: Atualizar o Sistema 🖥️ Primeiro, atualize seu sistema e instale o Tor: ```bash apt update apt install tor ``` --- ## Passo 2: Criar o Arquivo de Serviço `nrs.service` 🔧 Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo: ```unit [Unit] Description=Nostr Relay Server Service After=network.target [Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure [Install] WantedBy=multi-user.target ``` --- ## Passo 3: Baixar o Binário do Nostr 🚀 Baixe o binário mais recente do Nostr [aqui no GitHub]( https://github.com/gabrielmoura/SimpleNosrtRelay/releases). --- ## Passo 4: Criar as Pastas Necessárias 📂 Agora, crie as pastas para o aplicativo e o pendrive: ```bash mkdir -p /opt/nrs /mnt/edriver ``` --- ## Passo 5: Listar os Dispositivos Conectados 🔌 Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados: ```bash lsblk ``` --- ## Passo 6: Formatando o Pendrive 💾 Escolha o pendrive correto (por exemplo, `/dev/sda`) e formate-o: ```bash mkfs.vfat /dev/sda ``` --- ## Passo 7: Montar o Pendrive 💻 Monte o pendrive na pasta `/mnt/edriver`: ```bash mount /dev/sda /mnt/edriver ``` --- ## Passo 8: Verificar UUID dos Dispositivos 📋 Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados: ```bash blkid ``` --- ## Passo 9: Alterar o `fstab` para Montar o Pendrive Automáticamente 📝 Abra o arquivo `/etc/fstab` e adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim: ```fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0 ``` --- ## Passo 10: Copiar o Binário para a Pasta Correta 📥 Agora, copie o binário baixado para a pasta `/opt/nrs`: ```bash cp nrs-arm64 /opt/nrs ``` --- ## Passo 11: Criar o Arquivo de Configuração 🛠️ Crie o arquivo de configuração com o seguinte conteúdo e salve-o em `/opt/nrs/config.yaml`: ```yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true ``` --- ## Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️ Agora, copie o arquivo `nrs.service` para o diretório `/etc/systemd/system/`: ```bash cp nrs.service /etc/systemd/system/ ``` Recarregue os serviços e inicie o serviço `nrs`: ```bash systemctl daemon-reload systemctl enable --now nrs.service ``` --- ## Passo 13: Configurar o Tor 🌐 Abra o arquivo de configuração do Tor `/var/lib/tor/torrc` e adicione a seguinte linha: ```torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334 ``` --- ## Passo 14: Habilitar e Iniciar o Tor 🧅 Agora, ative e inicie o serviço Tor: ```bash systemctl enable --now tor.service ``` O Tor irá gerar um endereço `.onion` para o seu servidor Nostr. Você pode encontrá-lo no arquivo `/var/lib/tor/nostr_server/hostname`. --- ## Observações ⚠️ - Com essa configuração, **os dados serão salvos no pendrive**, enquanto o binário ficará no cartão SD do Raspberry Pi. - O endereço `.onion` do seu servidor Nostr será algo como: `ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion`. --- Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳 Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos. @ c582af78:698069cc
2025-02-13 01:04:26# **The Nine Orders of Angels: A Guide to the Celestial Hierarchy** When we think of angels, we often picture winged figures in flowing robes, guiding and protecting humanity. But the biblical and theological reality is far more complex—and often stranger—than these familiar depictions. The word *angel* comes from the Greek *angelos*, meaning “messenger,” but in scripture, angels serve a wide range of roles beyond delivering divine messages. Some are warriors wielding swords and leading celestial armies, others uphold the very throne of God, and some appear as multi-winged, multi-eyed beings beyond human comprehension. To bring order to this celestial realm, theologians—most notably Thomas Aquinas—classified angels into a hierarchy of **nine types**, divided into **three orders** based on their function and proximity to God. - **The lowest order** interacts with humanity. - **The middle order** governs spiritual and cosmic forces. - **The highest order** exists solely to serve and glorify God. Today, we explore these **nine ranks of angels**—from the familiar to the truly otherworldly. --- ## **I. The Third Order: Angels Who Interact with Humanity** *(The lowest tier of angels, closest to humans, acting as messengers and protectors.)* ### **1. Angels – The Messengers** https://image.nostr.build/b6462b67e14c8780896f465b664a521cdcdef7eb4b4314669b8d219aa36964c5.jpg These are the angels most commonly associated with divine guidance. According to Aquinas, every person has a **guardian angel**—an unseen protector guiding them through life. In *Genesis 28:12*, Jacob’s vision of a ladder stretching to Heaven shows angels ascending and descending, delivering messages and fulfilling divine commands. Some, like those who visited Abraham, even appeared as ordinary men, without wings or supernatural radiance. ### **2. Archangels – The Divine Enforcers** https://image.nostr.build/af8799efb61c5a64e958450bcd5aee55d2cade931cfc5ca7f0ae8745ccd4c45a.jpg Archangels carry out the most crucial missions in scripture. Gabriel announced the birth of Jesus to Mary, while Michael led the charge against Satan in the war for Heaven. Though only **Michael** is explicitly called an archangel in the Bible, tradition assigns this title to others, including **Raphael** and **Uriel**. Archangels serve as warriors and heralds, executing God’s most urgent decrees. ### **3. Principalities – Guardians of Nations** https://image.nostr.build/bc7cd78acb656be6c946da32244bfb9ecdfe9a7d1bd80e47eca764cae4a88b95.jpg Principalities oversee nations, cities, and communities, influencing their spiritual well-being. While they are not explicitly named in scripture, *Colossians 1:16* references “thrones, dominions, principalities, and powers.” Tradition suggests that Principalities guide earthly leaders, strengthening them in times of crisis—and perhaps even aiding biblical figures like King David in battle. --- ## **II. The Second Order: The Heavenly Governors** *(These angels reside in Heaven but influence earthly affairs, ensuring divine order is maintained.)* ### **4. Powers – The Celestial Warriors** https://image.nostr.build/1768abcbaefb2d1d21654a869b356d86a45d76a82197b9568528d4d4b9f0ef69.jpg Powers act as Heaven’s **military defenders**, guarding the spiritual realm from demonic forces. They are often depicted in armor, wielding weapons as they engage in cosmic battles. According to Christian tradition, Powers also **escort souls to Heaven**, ensuring their safe passage after death. Some believe that the battle between good and evil plays out, in part, through these celestial warriors. ### **5. Virtues – The Miracle Workers** https://image.nostr.build/b9a1e52f1dd4ef0f7e7dd198d81e7cd171eede8a64a40cac8176e12a5419aeba.jpg Virtues are associated with **miracles and nature**, regulating celestial phenomena and assisting in divine interventions. In Christian tradition, the two angels present at **Christ’s Ascension** are often considered Virtues, manifesting God’s power on Earth. ### **6. Dominions – The Angelic Rulers** https://image.nostr.build/0900d97bf545736e5edc1521f46a8afbf0e93fd81e472c88a56744ff0f56ce48.jpg Dominions do not typically interact with humans directly. Instead, they act as **commanders**, overseeing lower angels and ensuring divine order is maintained. They are described as serene, wise beings, often depicted holding golden staffs and orbs, symbolizing their authority and their close relationship with God. --- ## **III. The First Order: The Angels Closest to God** *(These angels exist solely to worship and serve God, residing in the highest realms of Heaven.)* ### **7. Thrones – The Wheels of God’s Chariot** https://image.nostr.build/d9f1e465129b138f4f960ee43ee9e06ceb3fd6f57e9658cd275e1ac1576b3c02.jpg Among the most mysterious angelic beings, Thrones are described in *Ezekiel’s vision* as **wheels covered in eyes, spinning within wheels**: > *“As I looked, I saw a wheel on the ground beside each creature with its four faces... Their rims were full of eyes all around. Wherever the spirit would go, they would go, because the spirit of the living creatures was in the wheels.”* > — *Ezekiel 1:15-21* Thrones serve as **God’s chariot**, supporting His throne and executing divine justice. Their strange, abstract form symbolizes stability and divine order. ### **8. Cherubim – The Guardians of Glory** https://image.nostr.build/e921ad4c32f56ebbb8f1bcb1ca2bc6eed1c736ec896429e008fc5b71cf2fd151.jpg Cherubim have been drastically misrepresented in art. Far from the **plump, childlike figures** seen in Renaissance paintings, the **biblical Cherubim** are **fearsome beings**. In *Ezekiel 10*, they are described as having **four faces**—a man, a lion, an ox, and an eagle—along with **four wings**. They also appear in *Genesis 3:24*, where they **guard the entrance to Eden with flaming swords** after Adam and Eve’s expulsion. https://image.nostr.build/f51286d4f35d9d6e85d8559600188ecc89a0969c3985814cae56cd230ea5db00.jpg Aquinas even suggested that **Satan himself was a fallen Cherub**. This theory is supported by *Ezekiel 28*, which describes an angelic being cast down from God’s presence: > *“You were anointed as a guardian cherub... You were blameless in your ways until wickedness was found in you... So I drove you in disgrace from the mount of God, and I expelled you, guardian cherub.”* > — *Ezekiel 28:14-17* ### **9. Seraphim – The Highest & Holiest** Seraphim stand **at the very throne of God**, continuously worshiping Him. In *Isaiah’s vision* (*Isaiah 6:1-7*), they are described as having **six wings**—two to fly, two to cover their feet, and two to cover their faces, symbolizing their humility before God. They sing: > **“Holy, holy, holy is the Lord of hosts; the whole earth is full of His glory.”** When Seraphim reappear in *Revelation*, their wings are now **covered in eyes**, representing divine omniscience. Their song shifts slightly: > *“Holy, holy, holy is the Lord God Almighty, who was and is and is to come!”* > — *Revelation 4:8* https://image.nostr.build/3495ccf6c0ba26b42d3e2b438ec19232cca148f6fbf29e5edd4129f5a198d05b.jpg Unlike other angelic beings, Seraphim do not interact with humans—they exist purely to **glorify God**. --- ## **“Be Not Afraid”** The angelic hierarchy provides a glimpse into the vast celestial order governing God’s universe. From the lowest messengers to the highest divine worshippers, each angelic being plays a unique role in the unfolding story of creation and salvation. Yet, despite their differences, there is one striking similarity across biblical encounters with angels: They often begin with a single phrase— **“Be not afraid.”**
@ c582af78:698069cc
2025-02-13 01:04:26# **The Nine Orders of Angels: A Guide to the Celestial Hierarchy** When we think of angels, we often picture winged figures in flowing robes, guiding and protecting humanity. But the biblical and theological reality is far more complex—and often stranger—than these familiar depictions. The word *angel* comes from the Greek *angelos*, meaning “messenger,” but in scripture, angels serve a wide range of roles beyond delivering divine messages. Some are warriors wielding swords and leading celestial armies, others uphold the very throne of God, and some appear as multi-winged, multi-eyed beings beyond human comprehension. To bring order to this celestial realm, theologians—most notably Thomas Aquinas—classified angels into a hierarchy of **nine types**, divided into **three orders** based on their function and proximity to God. - **The lowest order** interacts with humanity. - **The middle order** governs spiritual and cosmic forces. - **The highest order** exists solely to serve and glorify God. Today, we explore these **nine ranks of angels**—from the familiar to the truly otherworldly. --- ## **I. The Third Order: Angels Who Interact with Humanity** *(The lowest tier of angels, closest to humans, acting as messengers and protectors.)* ### **1. Angels – The Messengers** https://image.nostr.build/b6462b67e14c8780896f465b664a521cdcdef7eb4b4314669b8d219aa36964c5.jpg These are the angels most commonly associated with divine guidance. According to Aquinas, every person has a **guardian angel**—an unseen protector guiding them through life. In *Genesis 28:12*, Jacob’s vision of a ladder stretching to Heaven shows angels ascending and descending, delivering messages and fulfilling divine commands. Some, like those who visited Abraham, even appeared as ordinary men, without wings or supernatural radiance. ### **2. Archangels – The Divine Enforcers** https://image.nostr.build/af8799efb61c5a64e958450bcd5aee55d2cade931cfc5ca7f0ae8745ccd4c45a.jpg Archangels carry out the most crucial missions in scripture. Gabriel announced the birth of Jesus to Mary, while Michael led the charge against Satan in the war for Heaven. Though only **Michael** is explicitly called an archangel in the Bible, tradition assigns this title to others, including **Raphael** and **Uriel**. Archangels serve as warriors and heralds, executing God’s most urgent decrees. ### **3. Principalities – Guardians of Nations** https://image.nostr.build/bc7cd78acb656be6c946da32244bfb9ecdfe9a7d1bd80e47eca764cae4a88b95.jpg Principalities oversee nations, cities, and communities, influencing their spiritual well-being. While they are not explicitly named in scripture, *Colossians 1:16* references “thrones, dominions, principalities, and powers.” Tradition suggests that Principalities guide earthly leaders, strengthening them in times of crisis—and perhaps even aiding biblical figures like King David in battle. --- ## **II. The Second Order: The Heavenly Governors** *(These angels reside in Heaven but influence earthly affairs, ensuring divine order is maintained.)* ### **4. Powers – The Celestial Warriors** https://image.nostr.build/1768abcbaefb2d1d21654a869b356d86a45d76a82197b9568528d4d4b9f0ef69.jpg Powers act as Heaven’s **military defenders**, guarding the spiritual realm from demonic forces. They are often depicted in armor, wielding weapons as they engage in cosmic battles. According to Christian tradition, Powers also **escort souls to Heaven**, ensuring their safe passage after death. Some believe that the battle between good and evil plays out, in part, through these celestial warriors. ### **5. Virtues – The Miracle Workers** https://image.nostr.build/b9a1e52f1dd4ef0f7e7dd198d81e7cd171eede8a64a40cac8176e12a5419aeba.jpg Virtues are associated with **miracles and nature**, regulating celestial phenomena and assisting in divine interventions. In Christian tradition, the two angels present at **Christ’s Ascension** are often considered Virtues, manifesting God’s power on Earth. ### **6. Dominions – The Angelic Rulers** https://image.nostr.build/0900d97bf545736e5edc1521f46a8afbf0e93fd81e472c88a56744ff0f56ce48.jpg Dominions do not typically interact with humans directly. Instead, they act as **commanders**, overseeing lower angels and ensuring divine order is maintained. They are described as serene, wise beings, often depicted holding golden staffs and orbs, symbolizing their authority and their close relationship with God. --- ## **III. The First Order: The Angels Closest to God** *(These angels exist solely to worship and serve God, residing in the highest realms of Heaven.)* ### **7. Thrones – The Wheels of God’s Chariot** https://image.nostr.build/d9f1e465129b138f4f960ee43ee9e06ceb3fd6f57e9658cd275e1ac1576b3c02.jpg Among the most mysterious angelic beings, Thrones are described in *Ezekiel’s vision* as **wheels covered in eyes, spinning within wheels**: > *“As I looked, I saw a wheel on the ground beside each creature with its four faces... Their rims were full of eyes all around. Wherever the spirit would go, they would go, because the spirit of the living creatures was in the wheels.”* > — *Ezekiel 1:15-21* Thrones serve as **God’s chariot**, supporting His throne and executing divine justice. Their strange, abstract form symbolizes stability and divine order. ### **8. Cherubim – The Guardians of Glory** https://image.nostr.build/e921ad4c32f56ebbb8f1bcb1ca2bc6eed1c736ec896429e008fc5b71cf2fd151.jpg Cherubim have been drastically misrepresented in art. Far from the **plump, childlike figures** seen in Renaissance paintings, the **biblical Cherubim** are **fearsome beings**. In *Ezekiel 10*, they are described as having **four faces**—a man, a lion, an ox, and an eagle—along with **four wings**. They also appear in *Genesis 3:24*, where they **guard the entrance to Eden with flaming swords** after Adam and Eve’s expulsion. https://image.nostr.build/f51286d4f35d9d6e85d8559600188ecc89a0969c3985814cae56cd230ea5db00.jpg Aquinas even suggested that **Satan himself was a fallen Cherub**. This theory is supported by *Ezekiel 28*, which describes an angelic being cast down from God’s presence: > *“You were anointed as a guardian cherub... You were blameless in your ways until wickedness was found in you... So I drove you in disgrace from the mount of God, and I expelled you, guardian cherub.”* > — *Ezekiel 28:14-17* ### **9. Seraphim – The Highest & Holiest** Seraphim stand **at the very throne of God**, continuously worshiping Him. In *Isaiah’s vision* (*Isaiah 6:1-7*), they are described as having **six wings**—two to fly, two to cover their feet, and two to cover their faces, symbolizing their humility before God. They sing: > **“Holy, holy, holy is the Lord of hosts; the whole earth is full of His glory.”** When Seraphim reappear in *Revelation*, their wings are now **covered in eyes**, representing divine omniscience. Their song shifts slightly: > *“Holy, holy, holy is the Lord God Almighty, who was and is and is to come!”* > — *Revelation 4:8* https://image.nostr.build/3495ccf6c0ba26b42d3e2b438ec19232cca148f6fbf29e5edd4129f5a198d05b.jpg Unlike other angelic beings, Seraphim do not interact with humans—they exist purely to **glorify God**. --- ## **“Be Not Afraid”** The angelic hierarchy provides a glimpse into the vast celestial order governing God’s universe. From the lowest messengers to the highest divine worshippers, each angelic being plays a unique role in the unfolding story of creation and salvation. Yet, despite their differences, there is one striking similarity across biblical encounters with angels: They often begin with a single phrase— **“Be not afraid.”** @ b8851a06:9b120ba1
2025-01-14 15:28:32## **It Begins with a Click** It starts with a click: *“Do you agree to our terms and conditions?”*\ You scroll, you click, you comply. A harmless act, right? But what if every click was a surrender? What if every "yes" was another link in the chain binding you to a life where freedom requires approval? This is the age of permission. Every aspect of your life is mediated by gatekeepers. Governments demand forms, corporations demand clicks, and algorithms demand obedience. You’re free, of course, as long as you play by the rules. But who writes the rules? Who decides what’s allowed? Who owns your life? --- ## **Welcome to Digital Serfdom** We once imagined the internet as a digital frontier—a vast, open space where ideas could flow freely and innovation would know no bounds. But instead of creating a decentralized utopia, we built a new feudal system. - Your data? Owned by the lords of Big Tech. - Your money? Controlled by banks and bureaucrats who can freeze it on a whim. - Your thoughts? Filtered by algorithms that reward conformity and punish dissent. The modern internet is a land of serfs and lords, and guess who’s doing the farming? You. Every time you agree to the terms, accept the permissions, or let an algorithm decide for you, you till the fields of a system designed to control, not liberate. They don’t call it control, of course. They call it *“protection.”* They say, “We’re keeping you safe,” as they build a cage so big you can’t see the bars. --- ## **Freedom in Chains** But let’s be honest: we’re not just victims of this system—we’re participants. We’ve traded freedom for convenience, sovereignty for security. It’s easier to click “I Agree” than to read the fine print. It’s easier to let someone else hold your money than to take responsibility for it yourself. It’s easier to live a life of quiet compliance than to risk the chaos of true independence. We tell ourselves it’s no big deal. What’s one click? What’s one form? But the permissions pile up. The chains grow heavier. And one day, you wake up and realize you’re free to do exactly what the system allows—and nothing more. --- ## **The Great Unpermissioning** It doesn’t have to be this way. You don’t need their approval. You don’t need their systems. You don’t need their permission. The Great Unpermissioning is not a movement—it’s a mindset. It’s the refusal to accept a life mediated by gatekeepers. It’s the quiet rebellion of saying, *“No.”* It’s the realization that the freedom you seek won’t be granted—it must be reclaimed. - **Stop asking.** Permission is their tool. Refusal is your weapon. - **Start building.** Embrace tools that decentralize power: Bitcoin, encryption, open-source software, decentralized communication. Build systems they can’t control. - **Stand firm.** They’ll tell you it’s dangerous. They’ll call you a radical. But remember: the most dangerous thing you can do is comply. The path won’t be easy. Freedom never is. But it will be worth it. --- ## **The New Frontier** The age of permission has turned us into digital serfs, but there’s a new frontier on the horizon. It’s a world where you control your money, your data, your decisions. It’s a world of encryption, anonymity, and sovereignty. It’s a world built not on permission but on principles. This world won’t be given to you. You have to build it. You have to fight for it. And it starts with one simple act: refusing to comply. --- ## **A Final Word** They promised us safety, but what they delivered was submission. The age of permission has enslaved us to the mundane, the monitored, and the mediocre. The Great Unpermissioning isn’t about tearing down the old world—it’s about walking away from it. You don’t need to wait for their approval. You don’t need to ask for their permission. The freedom you’re looking for is already yours. Permission is their power—refusal is yours.
@ b8851a06:9b120ba1
2025-01-14 15:28:32## **It Begins with a Click** It starts with a click: *“Do you agree to our terms and conditions?”*\ You scroll, you click, you comply. A harmless act, right? But what if every click was a surrender? What if every "yes" was another link in the chain binding you to a life where freedom requires approval? This is the age of permission. Every aspect of your life is mediated by gatekeepers. Governments demand forms, corporations demand clicks, and algorithms demand obedience. You’re free, of course, as long as you play by the rules. But who writes the rules? Who decides what’s allowed? Who owns your life? --- ## **Welcome to Digital Serfdom** We once imagined the internet as a digital frontier—a vast, open space where ideas could flow freely and innovation would know no bounds. But instead of creating a decentralized utopia, we built a new feudal system. - Your data? Owned by the lords of Big Tech. - Your money? Controlled by banks and bureaucrats who can freeze it on a whim. - Your thoughts? Filtered by algorithms that reward conformity and punish dissent. The modern internet is a land of serfs and lords, and guess who’s doing the farming? You. Every time you agree to the terms, accept the permissions, or let an algorithm decide for you, you till the fields of a system designed to control, not liberate. They don’t call it control, of course. They call it *“protection.”* They say, “We’re keeping you safe,” as they build a cage so big you can’t see the bars. --- ## **Freedom in Chains** But let’s be honest: we’re not just victims of this system—we’re participants. We’ve traded freedom for convenience, sovereignty for security. It’s easier to click “I Agree” than to read the fine print. It’s easier to let someone else hold your money than to take responsibility for it yourself. It’s easier to live a life of quiet compliance than to risk the chaos of true independence. We tell ourselves it’s no big deal. What’s one click? What’s one form? But the permissions pile up. The chains grow heavier. And one day, you wake up and realize you’re free to do exactly what the system allows—and nothing more. --- ## **The Great Unpermissioning** It doesn’t have to be this way. You don’t need their approval. You don’t need their systems. You don’t need their permission. The Great Unpermissioning is not a movement—it’s a mindset. It’s the refusal to accept a life mediated by gatekeepers. It’s the quiet rebellion of saying, *“No.”* It’s the realization that the freedom you seek won’t be granted—it must be reclaimed. - **Stop asking.** Permission is their tool. Refusal is your weapon. - **Start building.** Embrace tools that decentralize power: Bitcoin, encryption, open-source software, decentralized communication. Build systems they can’t control. - **Stand firm.** They’ll tell you it’s dangerous. They’ll call you a radical. But remember: the most dangerous thing you can do is comply. The path won’t be easy. Freedom never is. But it will be worth it. --- ## **The New Frontier** The age of permission has turned us into digital serfs, but there’s a new frontier on the horizon. It’s a world where you control your money, your data, your decisions. It’s a world of encryption, anonymity, and sovereignty. It’s a world built not on permission but on principles. This world won’t be given to you. You have to build it. You have to fight for it. And it starts with one simple act: refusing to comply. --- ## **A Final Word** They promised us safety, but what they delivered was submission. The age of permission has enslaved us to the mundane, the monitored, and the mediocre. The Great Unpermissioning isn’t about tearing down the old world—it’s about walking away from it. You don’t need to wait for their approval. You don’t need to ask for their permission. The freedom you’re looking for is already yours. Permission is their power—refusal is yours. @ c582af78:698069cc
2025-02-13 01:03:50## **How to Be Happy: Aristotle’s Blueprint for a Flourishing Life** Everyone wants happiness. The problem? Most people don’t actually know what happiness is. Ask someone what would make them happy, and they’ll likely mention wealth, pleasure, success, or recognition. Over 2,000 years ago, Aristotle heard the same answers—and he rejected them. According to Aristotle, happiness isn’t something you *have*, but something you *do*. True happiness—what he called *eudaimonia*—isn’t about fleeting pleasures or external rewards. It’s about living well, cultivating virtue, and engaging deeply in life’s highest pursuits. So, what’s Aristotle’s formula for happiness? It comes down to three essential steps. --- ### **The False Paths to Happiness** Aristotle observed that most people chase happiness in three common ways: **wealth, pleasure, and honor**. While each has its appeal, none can sustain true fulfillment. Take **wealth**, for example. Money provides security and opportunity, but it doesn’t guarantee satisfaction. Aristotle noted that many people who seek wealth become obsessed with accumulating it rather than using it wisely. The result? An endless chase with no real contentment. **Pleasure** is even trickier. Aristotle acknowledged that pleasure is a natural good, but he warned against making it life’s ultimate goal. Living only for pleasure leads to a cycle of chasing temporary highs without ever achieving deeper fulfillment. As Aristotle put it, this is the life of *“fatted cattle”*—comfortable, but lacking excellence. Then there’s **honor**. Recognition feels good, but it depends on the approval of others. If you live solely for status, you risk valuing recognition over real achievement. Honor for its own sake is empty unless it’s tied to genuine virtue. **Aristotle’s conclusion?** These paths don’t lead to true happiness. They are distractions, not destinations. --- ### **The True Meaning of Happiness** If wealth, pleasure, and honor aren’t enough, then what *is* happiness? To answer that, we need to understand Aristotle’s term *eudaimonia*. Unlike our modern idea of happiness as a feeling, *eudaimonia* means **flourishing**—a life of purpose, virtue, and excellence. The key difference is that **wealth, pleasure, and honor are passive**—they happen *to* you. But *eudaimonia* is **active**—it’s something you cultivate through action. In his *Nicomachean Ethics*, Aristotle defines happiness as *“the activity of the soul in accordance with virtue.”* It’s not a prize to be won, but a way of living. A great example comes from sports. A skilled athlete doesn’t just sit around feeling happy—his joy comes from being *in motion*: training, competing, improving, and fully engaging in his craft. For Aristotle, happiness works the same way. It comes from actively developing your best qualities, not passively indulging in comfort. But how do you put this into practice? --- ## **Aristotle’s 3-Step Blueprint for a Good Life** Aristotle’s guide to happiness is surprisingly practical. Here’s how to apply it: ### **1. Cultivate Virtue Through Habit** Virtue isn’t something you’re born with—it’s something you practice. Just as an athlete trains for competition, you develop virtue by repeatedly choosing good actions. Courage, patience, and wisdom don’t just appear; they become part of you through habit. As Aristotle famously said: > **“We are what we repeatedly do. Excellence, then, is not an act, but a habit.”** Want to be generous? **Give more often.** Want to be disciplined? **Practice restraint.** Over time, these actions shape your character—and character shapes happiness. ### **2. Engage Fully in Meaningful Work** Happiness isn’t found in passivity, but in action. Aristotle believed that true fulfillment comes from using your talents to their fullest extent. This applies to everything from philosophy to craftsmanship to leadership. The key is **engagement**. Think of the satisfaction a musician feels while playing at their best, or the pride of a craftsman perfecting their work. These moments—where skill, effort, and purpose align—are true happiness in action. Contrary to popular belief, happiness isn’t about doing less. **It’s about doing the right things, with full commitment.** ### **3. Seek the Right Kind of Pleasure** Aristotle didn’t reject pleasure—he just emphasized choosing the *right* kind. Lower pleasures—like eating, drinking, or binge-watching TV—may feel good in the moment but often leave you feeling empty afterward. Higher pleasures—such as learning, mastering a craft, or cultivating meaningful relationships—lead to lasting fulfillment. The goal isn’t to reject pleasure, but to **align it with virtue**. Instead of chasing immediate gratification, seek pleasures that contribute to long-term flourishing. --- ## **Happiness as a Way of Life** It’s important to understand that happiness isn’t a destination—it’s a **practice**. It’s something cultivated daily by engaging in meaningful work, growing in virtue, and living with purpose. But most importantly, **happiness isn’t about what happens to you—it’s about who you become**. By cultivating *eudaimonia*, you change the essence of your being—just as a farmer who nurtures his crops becomes stronger through his labor. True happiness isn’t a fleeting emotion, but the natural result of a life well lived. The more you nurture virtue through action, the more deeply happiness takes root—until it becomes not just something you seek, but something you embody.
@ c582af78:698069cc
2025-02-13 01:03:50## **How to Be Happy: Aristotle’s Blueprint for a Flourishing Life** Everyone wants happiness. The problem? Most people don’t actually know what happiness is. Ask someone what would make them happy, and they’ll likely mention wealth, pleasure, success, or recognition. Over 2,000 years ago, Aristotle heard the same answers—and he rejected them. According to Aristotle, happiness isn’t something you *have*, but something you *do*. True happiness—what he called *eudaimonia*—isn’t about fleeting pleasures or external rewards. It’s about living well, cultivating virtue, and engaging deeply in life’s highest pursuits. So, what’s Aristotle’s formula for happiness? It comes down to three essential steps. --- ### **The False Paths to Happiness** Aristotle observed that most people chase happiness in three common ways: **wealth, pleasure, and honor**. While each has its appeal, none can sustain true fulfillment. Take **wealth**, for example. Money provides security and opportunity, but it doesn’t guarantee satisfaction. Aristotle noted that many people who seek wealth become obsessed with accumulating it rather than using it wisely. The result? An endless chase with no real contentment. **Pleasure** is even trickier. Aristotle acknowledged that pleasure is a natural good, but he warned against making it life’s ultimate goal. Living only for pleasure leads to a cycle of chasing temporary highs without ever achieving deeper fulfillment. As Aristotle put it, this is the life of *“fatted cattle”*—comfortable, but lacking excellence. Then there’s **honor**. Recognition feels good, but it depends on the approval of others. If you live solely for status, you risk valuing recognition over real achievement. Honor for its own sake is empty unless it’s tied to genuine virtue. **Aristotle’s conclusion?** These paths don’t lead to true happiness. They are distractions, not destinations. --- ### **The True Meaning of Happiness** If wealth, pleasure, and honor aren’t enough, then what *is* happiness? To answer that, we need to understand Aristotle’s term *eudaimonia*. Unlike our modern idea of happiness as a feeling, *eudaimonia* means **flourishing**—a life of purpose, virtue, and excellence. The key difference is that **wealth, pleasure, and honor are passive**—they happen *to* you. But *eudaimonia* is **active**—it’s something you cultivate through action. In his *Nicomachean Ethics*, Aristotle defines happiness as *“the activity of the soul in accordance with virtue.”* It’s not a prize to be won, but a way of living. A great example comes from sports. A skilled athlete doesn’t just sit around feeling happy—his joy comes from being *in motion*: training, competing, improving, and fully engaging in his craft. For Aristotle, happiness works the same way. It comes from actively developing your best qualities, not passively indulging in comfort. But how do you put this into practice? --- ## **Aristotle’s 3-Step Blueprint for a Good Life** Aristotle’s guide to happiness is surprisingly practical. Here’s how to apply it: ### **1. Cultivate Virtue Through Habit** Virtue isn’t something you’re born with—it’s something you practice. Just as an athlete trains for competition, you develop virtue by repeatedly choosing good actions. Courage, patience, and wisdom don’t just appear; they become part of you through habit. As Aristotle famously said: > **“We are what we repeatedly do. Excellence, then, is not an act, but a habit.”** Want to be generous? **Give more often.** Want to be disciplined? **Practice restraint.** Over time, these actions shape your character—and character shapes happiness. ### **2. Engage Fully in Meaningful Work** Happiness isn’t found in passivity, but in action. Aristotle believed that true fulfillment comes from using your talents to their fullest extent. This applies to everything from philosophy to craftsmanship to leadership. The key is **engagement**. Think of the satisfaction a musician feels while playing at their best, or the pride of a craftsman perfecting their work. These moments—where skill, effort, and purpose align—are true happiness in action. Contrary to popular belief, happiness isn’t about doing less. **It’s about doing the right things, with full commitment.** ### **3. Seek the Right Kind of Pleasure** Aristotle didn’t reject pleasure—he just emphasized choosing the *right* kind. Lower pleasures—like eating, drinking, or binge-watching TV—may feel good in the moment but often leave you feeling empty afterward. Higher pleasures—such as learning, mastering a craft, or cultivating meaningful relationships—lead to lasting fulfillment. The goal isn’t to reject pleasure, but to **align it with virtue**. Instead of chasing immediate gratification, seek pleasures that contribute to long-term flourishing. --- ## **Happiness as a Way of Life** It’s important to understand that happiness isn’t a destination—it’s a **practice**. It’s something cultivated daily by engaging in meaningful work, growing in virtue, and living with purpose. But most importantly, **happiness isn’t about what happens to you—it’s about who you become**. By cultivating *eudaimonia*, you change the essence of your being—just as a farmer who nurtures his crops becomes stronger through his labor. True happiness isn’t a fleeting emotion, but the natural result of a life well lived. The more you nurture virtue through action, the more deeply happiness takes root—until it becomes not just something you seek, but something you embody. @ 6389be64:ef439d32
2025-01-14 01:31:12Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin. I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy. Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing. # Smokey The Bear In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong. Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir! Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working. So, in a world of fire, what does an ally look like and what does it do? # Meet The Forest Walker  For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved. Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance. The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment. # The Small Branch Chipper  When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system. The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”. A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration. I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible. Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process. # The Gassifier  The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification? Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest. Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment. When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products. # Biochar: The Waste  Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here. Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process. Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself. The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations. # Wood Vinegar: More Waste  Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits. For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality. This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well). # The Internal Combustion Engine  Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system. The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget. # CO2 Production For Growth  Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure. An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil. The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly. The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees. # The Branch Drones  During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest. These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission. The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control. # The Bitcoin Miner  Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce? Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500? What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost? # The Mesh Network  What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other. Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining? # Back To The Chain  Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it. A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many. We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs. But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities. # Sensor Packages ### LiDaR  The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns. LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable. Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation. ### pH, Soil Moisture, and Cation Exchange Sensing  The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component. ### Weather Data  Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present. I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?” # Noise Suppression  Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise. It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount. # Fire Safety  A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly. # The Wrap  How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off. Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity. Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up. What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
@ 6389be64:ef439d32
2025-01-14 01:31:12Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin. I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy. Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing. # Smokey The Bear In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong. Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir! Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working. So, in a world of fire, what does an ally look like and what does it do? # Meet The Forest Walker  For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved. Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance. The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment. # The Small Branch Chipper  When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system. The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”. A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration. I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible. Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process. # The Gassifier  The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification? Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest. Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment. When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products. # Biochar: The Waste  Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here. Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process. Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself. The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations. # Wood Vinegar: More Waste  Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits. For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality. This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well). # The Internal Combustion Engine  Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system. The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget. # CO2 Production For Growth  Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure. An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil. The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly. The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees. # The Branch Drones  During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest. These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission. The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control. # The Bitcoin Miner  Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce? Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500? What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost? # The Mesh Network  What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other. Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining? # Back To The Chain  Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it. A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many. We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs. But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities. # Sensor Packages ### LiDaR  The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns. LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable. Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation. ### pH, Soil Moisture, and Cation Exchange Sensing  The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component. ### Weather Data  Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present. I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?” # Noise Suppression  Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise. It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount. # Fire Safety  A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly. # The Wrap  How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off. Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity. Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up. What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next. @ 57d1a264:69f1fee1
2025-02-13 00:28:45This past week, @erik_ and @Sushant have been working on improving the onboarding flow for [Sovran](https://sovranbitcoin.com/) bitcoin wallet. First revision on thee figma file below, would appreciate any feedback.   https://www.figma.com/design/inNLo6AaPMX26D3GumcXGC/UI%2FUX-Audit--Onboarding-User-Flow?node-id=0-1&t=Wl0EVhH5fJgYYSJI-1 If you want to review the UX audit of the current flow, see the feedback provided, and check Sushant's initial suggestions, you can do so here:  https://www.figma.com/board/Jfo4nLIKyR6lacokXze4Mv/Sovran-Onboarding-UX-Audit?node-id=0-1&t=gOZyo57zfeqxFXeB-1 originally posted at https://stacker.news/items/884272
@ 57d1a264:69f1fee1
2025-02-13 00:28:45This past week, @erik_ and @Sushant have been working on improving the onboarding flow for [Sovran](https://sovranbitcoin.com/) bitcoin wallet. First revision on thee figma file below, would appreciate any feedback.   https://www.figma.com/design/inNLo6AaPMX26D3GumcXGC/UI%2FUX-Audit--Onboarding-User-Flow?node-id=0-1&t=Wl0EVhH5fJgYYSJI-1 If you want to review the UX audit of the current flow, see the feedback provided, and check Sushant's initial suggestions, you can do so here:  https://www.figma.com/board/Jfo4nLIKyR6lacokXze4Mv/Sovran-Onboarding-UX-Audit?node-id=0-1&t=gOZyo57zfeqxFXeB-1 originally posted at https://stacker.news/items/884272 @ e3ba5e1a:5e433365
2025-01-13 16:47:27My blog posts and reading material have both been on a decidedly economics-heavy slant recently. The topic today, incentives, squarely falls into the category of economics. However, when I say economics, I’m not talking about “analyzing supply and demand curves.” I’m talking about the true basis of economics: understanding how human beings make decisions in a world of scarcity. A fair definition of incentive is “a reward or punishment that motivates behavior to achieve a desired outcome.” When most people think about economic incentives, they’re thinking of money. If I offer my son $5 if he washes the dishes, I’m incentivizing certain behavior. We can’t guarantee that he’ll do what I want him to do, but we can agree that the incentive structure itself will guide and ultimately determine what outcome will occur. The great thing about monetary incentives is how easy they are to talk about and compare. “Would I rather make $5 washing the dishes or $10 cleaning the gutters?” But much of the world is incentivized in non-monetary ways too. For example, using the “punishment” half of the definition above, I might threaten my son with losing Nintendo Switch access if he doesn’t wash the dishes. No money is involved, but I’m still incentivizing behavior. And there are plenty of incentives beyond our direct control\! My son is *also* incentivized to not wash dishes because it’s boring, or because he has some friends over that he wants to hang out with, or dozens of other things. Ultimately, the conflicting array of different incentive structures placed on him will ultimately determine what actions he chooses to take. ## Why incentives matter A phrase I see often in discussions—whether they are political, parenting, economic, or business—is “if they could **just** do…” Each time I see that phrase, I cringe a bit internally. Usually, the underlying assumption of the statement is “if people would behave contrary to their incentivized behavior then things would be better.” For example: * If my kids would just go to bed when I tell them, they wouldn’t be so cranky in the morning. * If people would just use the recycling bin, we wouldn’t have such a landfill problem. * If people would just stop being lazy, our team would deliver our project on time. In all these cases, the speakers are seemingly flummoxed as to why the people in question don’t behave more rationally. The problem is: each group is behaving perfectly rationally. * The kids have a high time preference, and care more about the joy of staying up now than the crankiness in the morning. Plus, they don’t really suffer the consequences of morning crankiness, their parents do. * No individual suffers much from their individual contribution to a landfill. If they stopped growing the size of the landfill, it would make an insignificant difference versus the amount of effort they need to engage in to properly recycle. * If a team doesn’t properly account for the productivity of individuals on a project, each individual receives less harm from their own inaction. Sure, the project may be delayed, company revenue may be down, and they may even risk losing their job when the company goes out of business. But their laziness individually won’t determine the entirety of that outcome. By contrast, they greatly benefit from being lazy by getting to relax at work, go on social media, read a book, or do whatever else they do when they’re supposed to be working.  My point here is that, as long as you ignore the reality of how incentives drive human behavior, you’ll fail at getting the outcomes you want. If everything I wrote up until now made perfect sense, you understand the premise of this blog post. The rest of it will focus on a bunch of real-world examples to hammer home the point, and demonstrate how versatile this mental model is. ## Running a company Let’s say I run my own company, with myself as the only employee. My personal revenue will be 100% determined by my own actions. If I decide to take Tuesday afternoon off and go fishing, I’ve chosen to lose that afternoon’s revenue. Implicitly, I’ve decided that the enjoyment I get from an afternoon of fishing is greater than the potential revenue. You may think I’m being lazy, but it’s my decision to make. In this situation, the incentive–money–is perfectly aligned with my actions. Compare this to a typical company/employee relationship. I might have a bank of Paid Time Off (PTO) days, in which case once again my incentives are relatively aligned. I know that I can take off 15 days throughout the year, and I’ve chosen to use half a day for the fishing trip. All is still good. What about unlimited time off? Suddenly incentives are starting to misalign. I don’t directly pay a price for not showing up to work on Tuesday. Or Wednesday as well, for that matter. I might ultimately be fired for not doing my job, but that will take longer to work its way through the system than simply not making any money for the day taken off. Compensation overall falls into this misaligned incentive structure. Let’s forget about taking time off. Instead, I work full time on a software project I’m assigned. But instead of using the normal toolchain we’re all used to at work, I play around with a new programming language. I get the fun and joy of playing with new technology, and potentially get to pad my resume a bit when I’m ready to look for a new job. But my current company gets slower results, less productivity, and is forced to subsidize my extracurricular learning. When a CEO has a bonus structure based on profitability, he’ll do everything he can to make the company profitable. This might include things that actually benefit the company, like improving product quality, reducing internal red tape, or finding cheaper vendors. But it might also include destructive practices, like slashing the R\&D budget to show massive profits this year, in exchange for a catastrophe next year when the next version of the product fails to ship.  Or my favorite example. My parents owned a business when I was growing up. They had a back office where they ran operations like accounting. All of the furniture was old couches from our house. After all, any money they spent on furniture came right out of their paychecks\! But in a large corporate environment, each department is generally given a budget for office furniture, a budget which doesn’t roll over year-to-year. The result? Executives make sure to spend the entire budget each year, often buying furniture far more expensive than they would choose if it was their own money. There are plenty of details you can quibble with above. It’s in a company’s best interest to give people downtime so that they can come back recharged. Having good ergonomic furniture can in fact increase productivity in excess of the money spent on it. But overall, the picture is pretty clear: in large corporate structures, you’re guaranteed to have mismatches between the company’s goals and the incentive structure placed on individuals. Using our model from above, we can lament how lazy, greedy, and unethical the employees are for doing what they’re incentivized to do instead of what’s right. But that’s simply ignoring the reality of human nature. # Moral hazard Moral hazard is a situation where one party is incentivized to take on more risk because another party will bear the consequences. Suppose I tell my son when he turns 21 (or whatever legal gambling age is) that I’ll cover all his losses for a day at the casino, but he gets to keep all the winnings. What do you think he’s going to do? The most logical course of action is to place the largest possible bets for as long as possible, asking me to cover each time he loses, and taking money off the table and into his bank account each time he wins.  But let’s look at a slightly more nuanced example. I go to a bathroom in the mall. As I’m leaving, I wash my hands. It will take me an extra 1 second to turn off the water when I’m done washing. That’s a trivial price to pay. If I *don’t* turn off the water, the mall will have to pay for many liters of wasted water, benefiting no one. But I won’t suffer any consequences at all. This is also a moral hazard, but most people will still turn off the water. Why? Usually due to some combination of other reasons such as: 1. We’re so habituated to turning off the water that we don’t even consider *not* turning it off. Put differently, the mental effort needed to not turn off the water is more expensive than the 1 second of time to turn it off. 2. Many of us have been brought up with a deep guilt about wasting resources like water. We have an internal incentive structure that makes the 1 second to turn off the water much less costly than the mental anguish of the waste we created. 3. We’re afraid we’ll be caught by someone else and face some kind of social repercussions. (Or maybe more than social. Are you sure there isn’t a law against leaving the water tap on?) Even with all that in place, you may notice that many public bathrooms use automatic water dispensers. Sure, there’s a sanitation reason for that, but it’s also to avoid this moral hazard. A common denominator in both of these is that the person taking the action that causes the liability (either the gambling or leaving the water on) is not the person who bears the responsibility for that liability (the father or the mall owner). Generally speaking, the closer together the person making the decision and the person incurring the liability are, the smaller the moral hazard. It’s easy to demonstrate that by extending the casino example a bit. I said it was the father who was covering the losses of the gambler. Many children (though not all) would want to avoid totally bankrupting their parents, or at least financially hurting them. Instead, imagine that someone from the IRS shows up at your door, hands you a credit card, and tells you you can use it at a casino all day, taking home all the chips you want. The money is coming from the government. How many people would put any restriction on how much they spend? And since we’re talking about the government already… ## Government moral hazards As I was preparing to write this blog post, the California wildfires hit. The discussions around those wildfires gave a *huge* number of examples of moral hazards. I decided to cherry-pick a few for this post. The first and most obvious one: California is asking for disaster relief funds from the federal government. That sounds wonderful. These fires were a natural disaster, so why shouldn’t the federal government pitch in and help take care of people? The problem is, once again, a moral hazard. In the case of the wildfires, California and Los Angeles both had ample actions they could have taken to mitigate the destruction of this fire: better forest management, larger fire department, keeping the water reservoirs filled, and probably much more that hasn’t come to light yet. If the federal government bails out California, it will be a clear message for the future: your mistakes will be fixed by others. You know what kind of behavior that incentivizes? More risky behavior\! Why spend state funds on forest management and extra firefighters—activities that don’t win politicians a lot of votes in general—when you could instead spend it on a football stadium, higher unemployment payments, or anything else, and then let the feds cover the cost of screw-ups. You may notice that this is virtually identical to the 2008 “too big to fail” bail-outs. Wall Street took insanely risky behavior, reaped huge profits for years, and when they eventually got caught with their pants down, the rest of us bailed them out. “Privatizing profits, socializing losses.”  And here’s the absolute best part of this: I can’t even truly blame either California *or* Wall Street. (I mean, I *do* blame them, I think their behavior is reprehensible, but you’ll see what I mean.) In a world where the rules of the game implicitly include the bail-out mentality, you would be harming your citizens/shareholders/investors if you didn’t engage in that risky behavior. Since everyone is on the hook for those socialized losses, your best bet is to maximize those privatized profits. There’s a lot more to government and moral hazard, but I think these two cases demonstrate the crux pretty solidly. But let’s leave moral hazard behind for a bit and get to general incentivization discussions. # Non-monetary competition At least 50% of the economics knowledge I have comes from the very first econ course I took in college. That professor was amazing, and had some very colorful stories. I can’t vouch for the veracity of the two I’m about to share, but they definitely drive the point home. In the 1970s, the US had an oil shortage. To “fix” this problem, they instituted price caps on gasoline, which of course resulted in insufficient gasoline. To “fix” this problem, they instituted policies where, depending on your license plate number, you could only fill up gas on certain days of the week. (Irrelevant detail for our point here, but this just resulted in people filling up their tanks more often, no reduction in gas usage.) Anyway, my professor’s wife had a friend. My professor described in *great* detail how attractive this woman was. I’ll skip those details here since this is a PG-rated blog. In any event, she never had any trouble filling up her gas tank any day of the week. She would drive up, be told she couldn’t fill up gas today, bat her eyes at the attendant, explain how helpless she was, and was always allowed to fill up gas. This is a demonstration of *non-monetary compensation*. Most of the time in a free market, capitalist economy, people are compensated through money. When price caps come into play, there’s a limit to how much monetary compensation someone can receive. And in that case, people find other ways of competing. Like this woman’s case: through using flirtatious behavior to compensate the gas station workers to let her cheat the rules. The other example was much more insidious. Santa Monica had a problem: it was predominantly wealthy and white. They wanted to fix this problem, and decided to put in place rent controls. After some time, they discovered that Santa Monica had become *wealthier and whiter*, the exact opposite of their desired outcome. Why would that happen? Someone investigated, and ended up interviewing a landlady that demonstrated the reason. She was an older white woman, and admittedly racist. Prior to the rent controls, she would list her apartments in the newspaper, and would be legally obligated to rent to anyone who could afford it. Once rent controls were in place, she took a different tact. She knew that she would only get a certain amount for the apartment, and that the demand for apartments was higher than the supply. That meant she could be picky. She ended up finding tenants through friends-of-friends. Since it wasn’t an official advertisement, she wasn’t legally required to rent it out if someone could afford to pay. Instead, she got to interview people individually and then make them an offer. Normally, that would have resulted in receiving a lower rental price, but not under rent controls. So who did she choose? A young, unmarried, wealthy, white woman. It made perfect sense. Women were less intimidating and more likely to maintain the apartment better. Wealthy people, she determined, would be better tenants. (I have no idea if this is true in practice or not, I’m not a landlord myself.) Unmarried, because no kids running around meant less damage to the property. And, of course, white. Because she was racist, and her incentive structure made her prefer whites. You can deride her for being racist, I won’t disagree with you. But it’s simply the reality. Under the non-rent-control scenario, her profit motive for money outweighed her racism motive. But under rent control, the monetary competition was removed, and she was free to play into her racist tendencies without facing any negative consequences. ## Bureaucracy These were the two examples I remember for that course. But non-monetary compensation pops up in many more places. One highly pertinent example is bureaucracies. Imagine you have a government office, or a large corporation’s acquisition department, or the team that apportions grants at a university. In all these cases, you have a group of people making decisions about handing out money that has no monetary impact on them. If they give to the best qualified recipients, they receive no raises. If they spend the money recklessly on frivolous projects, they face no consequences. Under such an incentivization scheme, there’s little to encourage the bureaucrats to make intelligent funding decisions. Instead, they’ll be incentivized to spend the money where they recognize non-monetary benefits. This is why it’s so common to hear about expensive meals, gift bags at conferences, and even more inappropriate ways of trying to curry favor with those that hold the purse strings. Compare that ever so briefly with the purchases made by a small mom-and-pop store like my parents owned. Could my dad take a bribe to buy from a vendor who’s ripping him off? Absolutely he could\! But he’d lose more on the deal than he’d make on the bribe, since he’s directly incentivized by the deal itself. It would make much more sense for him to go with the better vendor, save $5,000 on the deal, and then treat himself to a lavish $400 meal to celebrate. # Government incentivized behavior This post is getting longer in the tooth than I’d intended, so I’ll finish off with this section and make it a bit briefer. Beyond all the methods mentioned above, government has another mechanism for modifying behavior: through directly changing incentives via legislation, regulation, and monetary policy. Let’s see some examples: * Artificial modification of interest rates encourages people to take on more debt than they would in a free capital market, leading to [malinvestment](https://en.wikipedia.org/wiki/Malinvestment) and a consumer debt crisis, and causing the boom-bust cycle we all painfully experience. * Going along with that, giving tax breaks on interest payments further artificially incentivizes people to take on debt that they wouldn’t otherwise. * During COVID-19, at some points unemployment benefits were greater than minimum wage, incentivizing people to rather stay home and not work than get a job, leading to reduced overall productivity in the economy and more printed dollars for benefits. In other words, it was a perfect recipe for inflation. * The tax code gives deductions to “help” people. That might be true, but the real impact is incentivizing people to make decisions they wouldn’t have otherwise. For example, giving out tax deductions on children encourages having more kids. Tax deductions on childcare and preschools incentivizes dual-income households. Whether or not you like the outcomes, it’s clear that it’s government that’s encouraging these outcomes to happen. * Tax incentives cause people to engage in behavior they wouldn’t otherwise (daycare+working mother, for example). * Inflation means that the value of your money goes down over time, which encourages people to spend more today, when their money has a larger impact. (Milton Friedman described this as [high living](https://www.youtube.com/watch?v=ZwNDd2_beTU).) # Conclusion The idea here is simple, and fully encapsulated in the title: incentives determine outcomes. If you want to know how to get a certain outcome from others, incentivize them to want that to happen. If you want to understand why people act in seemingly irrational ways, check their incentives. If you’re confused why leaders (and especially politicians) seem to engage in destructive behavior, check their incentives. We can bemoan these realities all we want, but they *are* realities. While there are some people who have a solid internal moral and ethical code, and that internal code incentivizes them to behave against their externally-incentivized interests, those people are rare. And frankly, those people are self-defeating. People *should* take advantage of the incentives around them. Because if they don’t, someone else will. (If you want a literary example of that last comment, see the horse in Animal Farm.) How do we improve the world under these conditions? Make sure the incentives align well with the overall goals of society. To me, it’s a simple formula: * Focus on free trade, value for value, as the basis of a society. In that system, people are always incentivized to provide value to other people. * Reduce the size of bureaucracies and large groups of all kinds. The larger an organization becomes, the farther the consequences of decisions are from those who make them. * And since the nature of human beings will be to try and create areas where they can control the incentive systems to their own benefits, make that as difficult as possible. That comes in the form of strict limits on government power, for example. And even if you don’t want to buy in to this conclusion, I hope the rest of the content was educational, and maybe a bit entertaining\!
@ e3ba5e1a:5e433365
2025-01-13 16:47:27My blog posts and reading material have both been on a decidedly economics-heavy slant recently. The topic today, incentives, squarely falls into the category of economics. However, when I say economics, I’m not talking about “analyzing supply and demand curves.” I’m talking about the true basis of economics: understanding how human beings make decisions in a world of scarcity. A fair definition of incentive is “a reward or punishment that motivates behavior to achieve a desired outcome.” When most people think about economic incentives, they’re thinking of money. If I offer my son $5 if he washes the dishes, I’m incentivizing certain behavior. We can’t guarantee that he’ll do what I want him to do, but we can agree that the incentive structure itself will guide and ultimately determine what outcome will occur. The great thing about monetary incentives is how easy they are to talk about and compare. “Would I rather make $5 washing the dishes or $10 cleaning the gutters?” But much of the world is incentivized in non-monetary ways too. For example, using the “punishment” half of the definition above, I might threaten my son with losing Nintendo Switch access if he doesn’t wash the dishes. No money is involved, but I’m still incentivizing behavior. And there are plenty of incentives beyond our direct control\! My son is *also* incentivized to not wash dishes because it’s boring, or because he has some friends over that he wants to hang out with, or dozens of other things. Ultimately, the conflicting array of different incentive structures placed on him will ultimately determine what actions he chooses to take. ## Why incentives matter A phrase I see often in discussions—whether they are political, parenting, economic, or business—is “if they could **just** do…” Each time I see that phrase, I cringe a bit internally. Usually, the underlying assumption of the statement is “if people would behave contrary to their incentivized behavior then things would be better.” For example: * If my kids would just go to bed when I tell them, they wouldn’t be so cranky in the morning. * If people would just use the recycling bin, we wouldn’t have such a landfill problem. * If people would just stop being lazy, our team would deliver our project on time. In all these cases, the speakers are seemingly flummoxed as to why the people in question don’t behave more rationally. The problem is: each group is behaving perfectly rationally. * The kids have a high time preference, and care more about the joy of staying up now than the crankiness in the morning. Plus, they don’t really suffer the consequences of morning crankiness, their parents do. * No individual suffers much from their individual contribution to a landfill. If they stopped growing the size of the landfill, it would make an insignificant difference versus the amount of effort they need to engage in to properly recycle. * If a team doesn’t properly account for the productivity of individuals on a project, each individual receives less harm from their own inaction. Sure, the project may be delayed, company revenue may be down, and they may even risk losing their job when the company goes out of business. But their laziness individually won’t determine the entirety of that outcome. By contrast, they greatly benefit from being lazy by getting to relax at work, go on social media, read a book, or do whatever else they do when they’re supposed to be working.  My point here is that, as long as you ignore the reality of how incentives drive human behavior, you’ll fail at getting the outcomes you want. If everything I wrote up until now made perfect sense, you understand the premise of this blog post. The rest of it will focus on a bunch of real-world examples to hammer home the point, and demonstrate how versatile this mental model is. ## Running a company Let’s say I run my own company, with myself as the only employee. My personal revenue will be 100% determined by my own actions. If I decide to take Tuesday afternoon off and go fishing, I’ve chosen to lose that afternoon’s revenue. Implicitly, I’ve decided that the enjoyment I get from an afternoon of fishing is greater than the potential revenue. You may think I’m being lazy, but it’s my decision to make. In this situation, the incentive–money–is perfectly aligned with my actions. Compare this to a typical company/employee relationship. I might have a bank of Paid Time Off (PTO) days, in which case once again my incentives are relatively aligned. I know that I can take off 15 days throughout the year, and I’ve chosen to use half a day for the fishing trip. All is still good. What about unlimited time off? Suddenly incentives are starting to misalign. I don’t directly pay a price for not showing up to work on Tuesday. Or Wednesday as well, for that matter. I might ultimately be fired for not doing my job, but that will take longer to work its way through the system than simply not making any money for the day taken off. Compensation overall falls into this misaligned incentive structure. Let’s forget about taking time off. Instead, I work full time on a software project I’m assigned. But instead of using the normal toolchain we’re all used to at work, I play around with a new programming language. I get the fun and joy of playing with new technology, and potentially get to pad my resume a bit when I’m ready to look for a new job. But my current company gets slower results, less productivity, and is forced to subsidize my extracurricular learning. When a CEO has a bonus structure based on profitability, he’ll do everything he can to make the company profitable. This might include things that actually benefit the company, like improving product quality, reducing internal red tape, or finding cheaper vendors. But it might also include destructive practices, like slashing the R\&D budget to show massive profits this year, in exchange for a catastrophe next year when the next version of the product fails to ship.  Or my favorite example. My parents owned a business when I was growing up. They had a back office where they ran operations like accounting. All of the furniture was old couches from our house. After all, any money they spent on furniture came right out of their paychecks\! But in a large corporate environment, each department is generally given a budget for office furniture, a budget which doesn’t roll over year-to-year. The result? Executives make sure to spend the entire budget each year, often buying furniture far more expensive than they would choose if it was their own money. There are plenty of details you can quibble with above. It’s in a company’s best interest to give people downtime so that they can come back recharged. Having good ergonomic furniture can in fact increase productivity in excess of the money spent on it. But overall, the picture is pretty clear: in large corporate structures, you’re guaranteed to have mismatches between the company’s goals and the incentive structure placed on individuals. Using our model from above, we can lament how lazy, greedy, and unethical the employees are for doing what they’re incentivized to do instead of what’s right. But that’s simply ignoring the reality of human nature. # Moral hazard Moral hazard is a situation where one party is incentivized to take on more risk because another party will bear the consequences. Suppose I tell my son when he turns 21 (or whatever legal gambling age is) that I’ll cover all his losses for a day at the casino, but he gets to keep all the winnings. What do you think he’s going to do? The most logical course of action is to place the largest possible bets for as long as possible, asking me to cover each time he loses, and taking money off the table and into his bank account each time he wins.  But let’s look at a slightly more nuanced example. I go to a bathroom in the mall. As I’m leaving, I wash my hands. It will take me an extra 1 second to turn off the water when I’m done washing. That’s a trivial price to pay. If I *don’t* turn off the water, the mall will have to pay for many liters of wasted water, benefiting no one. But I won’t suffer any consequences at all. This is also a moral hazard, but most people will still turn off the water. Why? Usually due to some combination of other reasons such as: 1. We’re so habituated to turning off the water that we don’t even consider *not* turning it off. Put differently, the mental effort needed to not turn off the water is more expensive than the 1 second of time to turn it off. 2. Many of us have been brought up with a deep guilt about wasting resources like water. We have an internal incentive structure that makes the 1 second to turn off the water much less costly than the mental anguish of the waste we created. 3. We’re afraid we’ll be caught by someone else and face some kind of social repercussions. (Or maybe more than social. Are you sure there isn’t a law against leaving the water tap on?) Even with all that in place, you may notice that many public bathrooms use automatic water dispensers. Sure, there’s a sanitation reason for that, but it’s also to avoid this moral hazard. A common denominator in both of these is that the person taking the action that causes the liability (either the gambling or leaving the water on) is not the person who bears the responsibility for that liability (the father or the mall owner). Generally speaking, the closer together the person making the decision and the person incurring the liability are, the smaller the moral hazard. It’s easy to demonstrate that by extending the casino example a bit. I said it was the father who was covering the losses of the gambler. Many children (though not all) would want to avoid totally bankrupting their parents, or at least financially hurting them. Instead, imagine that someone from the IRS shows up at your door, hands you a credit card, and tells you you can use it at a casino all day, taking home all the chips you want. The money is coming from the government. How many people would put any restriction on how much they spend? And since we’re talking about the government already… ## Government moral hazards As I was preparing to write this blog post, the California wildfires hit. The discussions around those wildfires gave a *huge* number of examples of moral hazards. I decided to cherry-pick a few for this post. The first and most obvious one: California is asking for disaster relief funds from the federal government. That sounds wonderful. These fires were a natural disaster, so why shouldn’t the federal government pitch in and help take care of people? The problem is, once again, a moral hazard. In the case of the wildfires, California and Los Angeles both had ample actions they could have taken to mitigate the destruction of this fire: better forest management, larger fire department, keeping the water reservoirs filled, and probably much more that hasn’t come to light yet. If the federal government bails out California, it will be a clear message for the future: your mistakes will be fixed by others. You know what kind of behavior that incentivizes? More risky behavior\! Why spend state funds on forest management and extra firefighters—activities that don’t win politicians a lot of votes in general—when you could instead spend it on a football stadium, higher unemployment payments, or anything else, and then let the feds cover the cost of screw-ups. You may notice that this is virtually identical to the 2008 “too big to fail” bail-outs. Wall Street took insanely risky behavior, reaped huge profits for years, and when they eventually got caught with their pants down, the rest of us bailed them out. “Privatizing profits, socializing losses.”  And here’s the absolute best part of this: I can’t even truly blame either California *or* Wall Street. (I mean, I *do* blame them, I think their behavior is reprehensible, but you’ll see what I mean.) In a world where the rules of the game implicitly include the bail-out mentality, you would be harming your citizens/shareholders/investors if you didn’t engage in that risky behavior. Since everyone is on the hook for those socialized losses, your best bet is to maximize those privatized profits. There’s a lot more to government and moral hazard, but I think these two cases demonstrate the crux pretty solidly. But let’s leave moral hazard behind for a bit and get to general incentivization discussions. # Non-monetary competition At least 50% of the economics knowledge I have comes from the very first econ course I took in college. That professor was amazing, and had some very colorful stories. I can’t vouch for the veracity of the two I’m about to share, but they definitely drive the point home. In the 1970s, the US had an oil shortage. To “fix” this problem, they instituted price caps on gasoline, which of course resulted in insufficient gasoline. To “fix” this problem, they instituted policies where, depending on your license plate number, you could only fill up gas on certain days of the week. (Irrelevant detail for our point here, but this just resulted in people filling up their tanks more often, no reduction in gas usage.) Anyway, my professor’s wife had a friend. My professor described in *great* detail how attractive this woman was. I’ll skip those details here since this is a PG-rated blog. In any event, she never had any trouble filling up her gas tank any day of the week. She would drive up, be told she couldn’t fill up gas today, bat her eyes at the attendant, explain how helpless she was, and was always allowed to fill up gas. This is a demonstration of *non-monetary compensation*. Most of the time in a free market, capitalist economy, people are compensated through money. When price caps come into play, there’s a limit to how much monetary compensation someone can receive. And in that case, people find other ways of competing. Like this woman’s case: through using flirtatious behavior to compensate the gas station workers to let her cheat the rules. The other example was much more insidious. Santa Monica had a problem: it was predominantly wealthy and white. They wanted to fix this problem, and decided to put in place rent controls. After some time, they discovered that Santa Monica had become *wealthier and whiter*, the exact opposite of their desired outcome. Why would that happen? Someone investigated, and ended up interviewing a landlady that demonstrated the reason. She was an older white woman, and admittedly racist. Prior to the rent controls, she would list her apartments in the newspaper, and would be legally obligated to rent to anyone who could afford it. Once rent controls were in place, she took a different tact. She knew that she would only get a certain amount for the apartment, and that the demand for apartments was higher than the supply. That meant she could be picky. She ended up finding tenants through friends-of-friends. Since it wasn’t an official advertisement, she wasn’t legally required to rent it out if someone could afford to pay. Instead, she got to interview people individually and then make them an offer. Normally, that would have resulted in receiving a lower rental price, but not under rent controls. So who did she choose? A young, unmarried, wealthy, white woman. It made perfect sense. Women were less intimidating and more likely to maintain the apartment better. Wealthy people, she determined, would be better tenants. (I have no idea if this is true in practice or not, I’m not a landlord myself.) Unmarried, because no kids running around meant less damage to the property. And, of course, white. Because she was racist, and her incentive structure made her prefer whites. You can deride her for being racist, I won’t disagree with you. But it’s simply the reality. Under the non-rent-control scenario, her profit motive for money outweighed her racism motive. But under rent control, the monetary competition was removed, and she was free to play into her racist tendencies without facing any negative consequences. ## Bureaucracy These were the two examples I remember for that course. But non-monetary compensation pops up in many more places. One highly pertinent example is bureaucracies. Imagine you have a government office, or a large corporation’s acquisition department, or the team that apportions grants at a university. In all these cases, you have a group of people making decisions about handing out money that has no monetary impact on them. If they give to the best qualified recipients, they receive no raises. If they spend the money recklessly on frivolous projects, they face no consequences. Under such an incentivization scheme, there’s little to encourage the bureaucrats to make intelligent funding decisions. Instead, they’ll be incentivized to spend the money where they recognize non-monetary benefits. This is why it’s so common to hear about expensive meals, gift bags at conferences, and even more inappropriate ways of trying to curry favor with those that hold the purse strings. Compare that ever so briefly with the purchases made by a small mom-and-pop store like my parents owned. Could my dad take a bribe to buy from a vendor who’s ripping him off? Absolutely he could\! But he’d lose more on the deal than he’d make on the bribe, since he’s directly incentivized by the deal itself. It would make much more sense for him to go with the better vendor, save $5,000 on the deal, and then treat himself to a lavish $400 meal to celebrate. # Government incentivized behavior This post is getting longer in the tooth than I’d intended, so I’ll finish off with this section and make it a bit briefer. Beyond all the methods mentioned above, government has another mechanism for modifying behavior: through directly changing incentives via legislation, regulation, and monetary policy. Let’s see some examples: * Artificial modification of interest rates encourages people to take on more debt than they would in a free capital market, leading to [malinvestment](https://en.wikipedia.org/wiki/Malinvestment) and a consumer debt crisis, and causing the boom-bust cycle we all painfully experience. * Going along with that, giving tax breaks on interest payments further artificially incentivizes people to take on debt that they wouldn’t otherwise. * During COVID-19, at some points unemployment benefits were greater than minimum wage, incentivizing people to rather stay home and not work than get a job, leading to reduced overall productivity in the economy and more printed dollars for benefits. In other words, it was a perfect recipe for inflation. * The tax code gives deductions to “help” people. That might be true, but the real impact is incentivizing people to make decisions they wouldn’t have otherwise. For example, giving out tax deductions on children encourages having more kids. Tax deductions on childcare and preschools incentivizes dual-income households. Whether or not you like the outcomes, it’s clear that it’s government that’s encouraging these outcomes to happen. * Tax incentives cause people to engage in behavior they wouldn’t otherwise (daycare+working mother, for example). * Inflation means that the value of your money goes down over time, which encourages people to spend more today, when their money has a larger impact. (Milton Friedman described this as [high living](https://www.youtube.com/watch?v=ZwNDd2_beTU).) # Conclusion The idea here is simple, and fully encapsulated in the title: incentives determine outcomes. If you want to know how to get a certain outcome from others, incentivize them to want that to happen. If you want to understand why people act in seemingly irrational ways, check their incentives. If you’re confused why leaders (and especially politicians) seem to engage in destructive behavior, check their incentives. We can bemoan these realities all we want, but they *are* realities. While there are some people who have a solid internal moral and ethical code, and that internal code incentivizes them to behave against their externally-incentivized interests, those people are rare. And frankly, those people are self-defeating. People *should* take advantage of the incentives around them. Because if they don’t, someone else will. (If you want a literary example of that last comment, see the horse in Animal Farm.) How do we improve the world under these conditions? Make sure the incentives align well with the overall goals of society. To me, it’s a simple formula: * Focus on free trade, value for value, as the basis of a society. In that system, people are always incentivized to provide value to other people. * Reduce the size of bureaucracies and large groups of all kinds. The larger an organization becomes, the farther the consequences of decisions are from those who make them. * And since the nature of human beings will be to try and create areas where they can control the incentive systems to their own benefits, make that as difficult as possible. That comes in the form of strict limits on government power, for example. And even if you don’t want to buy in to this conclusion, I hope the rest of the content was educational, and maybe a bit entertaining\! @ 5579d5c0:db104ded
2025-02-12 23:41:09Most people think their metabolism is "broken" because they can't lose weight, feel sluggish, or gain fat easily. The truth? **Your metabolism isn’t broken, it’s just out of sync.** Your body doesn’t just burn calories randomly. It follows a natural **24-hour rhythm**, dictated by light exposure, movement, meal timing, and sleep. When these cues are off, your metabolism becomes dysfunctional. The good news? You don’t need to diet harder or exercise more. **You need to realign your metabolism with your body’s natural rhythm.** --- ### Why your metabolism feels “broken” Your body is designed to run on **timing signals, when to eat, when to move, when to rest**. Modern life disrupts these natural rhythms, leading to: **→ Low energy & afternoon crashes**: Skipping morning sunlight and staying indoors all day. **→ Stubborn belly fat & slow fat loss**: Eating at the wrong times, late-night snacking, and chronic stress. **→ Constant cravings & hunger:** Poor meal timing and eating foods that spike blood sugar too often. **→ Poor sleep & recovery**: Late night screen use, artificial light, and erratic bedtimes. The problem **isn’t your metabolism, it’s your environment and habits.** --- ### How to reset your metabolism naturally You don’t need extreme diets, calorie counting, or hours in the gym. Instead, **align your metabolism with your body’s natural timing signals** by focusing on these fundamentals: ### 1. Get natural light first thing in the morning Light in the first 30 minutes after waking sets your circadian rhythm (body clock), kickstarts hormone production, and improves insulin sensitivity. This simple habit helps to regulate hunger, energy, and fat-burning. **Action step:** Step outside for at least 5–10 minutes within 30 minutes of waking, no sunglasses, no contacts, only natural light exposure and take regular outdoor breaks during the day. --- ### 2. Stop eating late at night Eating late, especially high-carb/high-fat meals, signals your body to store fat instead of burning it. Late-night eating also disrupts sleep, which further impairs fat loss. **Action step:** Keep meals within a **10-12 hour eating window**, preferably between sunrise and sunset. **No snacking**. Finish your last meal **at least 3 hours before bed**. --- ### 3. Move throughout the day (Not just at the gym) Your metabolism isn’t just about burning calories, it’s about **how efficiently your body uses energy**. Sitting for long hours disrupts metabolic function, even if you work out later. **Action step:** Take a **5-minute movement break** every 1–2 hours. Stand, stretch, or better still go for a quick walk outside. --- ### 4. Prioritise deep, uninterrupted sleep Your body **burns fat and repairs muscle while you sleep**. Poor sleep increases hunger hormones (Ghrelin), prevents Leptin from working properly, and makes you crave junk food the next day. **Action step:** Dim lights after sunset, wear blue light blocking glasses, avoid screens 30-60 minutes before bed, and aim for **7.5-9 hours of quality sleep**. --- ### 5. Eat nutrient-dense foods What you eat matters, but **when** you eat it matters just as much. Front-loading protein and nutrients earlier in the day supports fat-burning and stabilises energy. **Action step:** Eat a **high-protein, nutrient-dense breakfast** and **avoid refined carbs & sugar, especially in the morning,** to prevent cravings later. --- Your metabolism isn’t broken, it’s just out of sync. Instead of obsessing over calories, **focus on realigning your body with its natural rhythms**: → **Morning sunlight** to set your metabolism for the day. → **Aligned meal timing** by eating during daylight & avoiding late-night eating. → **Frequent movement** to prevents metabolic slowdown from sitting. → **Quality sleep** which regulates fat-burning and hunger hormones. → **Nutrient-dense eating** giving your body what it needs. Fix your metabolism without dieting harder, just live in sync with how your body is designed to function. \-Chris --- If you want a simple methodical approach to fixing your metabolism, Let’s talk. **Book a free call here:** [**https://calendly.com/hello-chrispatrick**](https://calendly.com/hello-chrispatrick) **Follow me on Nostr**: [**https://primal.net/chrispatrick**](https://primal.net/chrispatrick) or [***nostr:npub124uatsq6pv74trzwvt34y4sx2z0uflhse7tkrv0pl69e8kcsfhkse30zsu***](https://primal.net/chrispatrick/npub124uatsq6pv74trzwvt34y4sx2z0uflhse7tkrv0pl69e8kcsfhkse30zsu)
@ 5579d5c0:db104ded
2025-02-12 23:41:09Most people think their metabolism is "broken" because they can't lose weight, feel sluggish, or gain fat easily. The truth? **Your metabolism isn’t broken, it’s just out of sync.** Your body doesn’t just burn calories randomly. It follows a natural **24-hour rhythm**, dictated by light exposure, movement, meal timing, and sleep. When these cues are off, your metabolism becomes dysfunctional. The good news? You don’t need to diet harder or exercise more. **You need to realign your metabolism with your body’s natural rhythm.** --- ### Why your metabolism feels “broken” Your body is designed to run on **timing signals, when to eat, when to move, when to rest**. Modern life disrupts these natural rhythms, leading to: **→ Low energy & afternoon crashes**: Skipping morning sunlight and staying indoors all day. **→ Stubborn belly fat & slow fat loss**: Eating at the wrong times, late-night snacking, and chronic stress. **→ Constant cravings & hunger:** Poor meal timing and eating foods that spike blood sugar too often. **→ Poor sleep & recovery**: Late night screen use, artificial light, and erratic bedtimes. The problem **isn’t your metabolism, it’s your environment and habits.** --- ### How to reset your metabolism naturally You don’t need extreme diets, calorie counting, or hours in the gym. Instead, **align your metabolism with your body’s natural timing signals** by focusing on these fundamentals: ### 1. Get natural light first thing in the morning Light in the first 30 minutes after waking sets your circadian rhythm (body clock), kickstarts hormone production, and improves insulin sensitivity. This simple habit helps to regulate hunger, energy, and fat-burning. **Action step:** Step outside for at least 5–10 minutes within 30 minutes of waking, no sunglasses, no contacts, only natural light exposure and take regular outdoor breaks during the day. --- ### 2. Stop eating late at night Eating late, especially high-carb/high-fat meals, signals your body to store fat instead of burning it. Late-night eating also disrupts sleep, which further impairs fat loss. **Action step:** Keep meals within a **10-12 hour eating window**, preferably between sunrise and sunset. **No snacking**. Finish your last meal **at least 3 hours before bed**. --- ### 3. Move throughout the day (Not just at the gym) Your metabolism isn’t just about burning calories, it’s about **how efficiently your body uses energy**. Sitting for long hours disrupts metabolic function, even if you work out later. **Action step:** Take a **5-minute movement break** every 1–2 hours. Stand, stretch, or better still go for a quick walk outside. --- ### 4. Prioritise deep, uninterrupted sleep Your body **burns fat and repairs muscle while you sleep**. Poor sleep increases hunger hormones (Ghrelin), prevents Leptin from working properly, and makes you crave junk food the next day. **Action step:** Dim lights after sunset, wear blue light blocking glasses, avoid screens 30-60 minutes before bed, and aim for **7.5-9 hours of quality sleep**. --- ### 5. Eat nutrient-dense foods What you eat matters, but **when** you eat it matters just as much. Front-loading protein and nutrients earlier in the day supports fat-burning and stabilises energy. **Action step:** Eat a **high-protein, nutrient-dense breakfast** and **avoid refined carbs & sugar, especially in the morning,** to prevent cravings later. --- Your metabolism isn’t broken, it’s just out of sync. Instead of obsessing over calories, **focus on realigning your body with its natural rhythms**: → **Morning sunlight** to set your metabolism for the day. → **Aligned meal timing** by eating during daylight & avoiding late-night eating. → **Frequent movement** to prevents metabolic slowdown from sitting. → **Quality sleep** which regulates fat-burning and hunger hormones. → **Nutrient-dense eating** giving your body what it needs. Fix your metabolism without dieting harder, just live in sync with how your body is designed to function. \-Chris --- If you want a simple methodical approach to fixing your metabolism, Let’s talk. **Book a free call here:** [**https://calendly.com/hello-chrispatrick**](https://calendly.com/hello-chrispatrick) **Follow me on Nostr**: [**https://primal.net/chrispatrick**](https://primal.net/chrispatrick) or [***nostr:npub124uatsq6pv74trzwvt34y4sx2z0uflhse7tkrv0pl69e8kcsfhkse30zsu***](https://primal.net/chrispatrick/npub124uatsq6pv74trzwvt34y4sx2z0uflhse7tkrv0pl69e8kcsfhkse30zsu) @ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs ## The reason why we have broken money Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world. In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes. However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore. Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too. Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it. ## Bitcoin overcomes the "transfer of hard money" problem Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design. Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it. Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive. Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold. ## Bitcoin blurs the line between commodity and technology Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules. At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable. Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases. ## The dangers of derivatives A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold. In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin. Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense. ## Learn for yourself If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody". There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
@ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs ## The reason why we have broken money Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world. In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes. However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore. Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too. Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it. ## Bitcoin overcomes the "transfer of hard money" problem Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design. Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it. Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive. Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold. ## Bitcoin blurs the line between commodity and technology Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules. At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable. Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases. ## The dangers of derivatives A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold. In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin. Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense. ## Learn for yourself If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody". There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance. @ 3b7fc823:e194354f
2025-02-12 23:13:57**Staying Digitally Safe in Airports: A Comprehensive Guide** Airports are hubs of activity, but they’re also places where your digital security can be at risk. From public Wi-Fi to potential device thefts, staying safe while traveling can feel overwhelming. However, with the right knowledge and precautions, you can protect yourself and enjoy your journey stress-free. Let’s dive into how to stay digitally safe in airports while traveling. --- ### **Understanding the Risks** 1. **Public Wi-Fi Vulnerabilities:** - Airports often offer free Wi-Fi, but these networks can be unsecured or insecure. Hackers may use these networks to intercept sensitive data. - Avoid using public Wi-Fi for personal banking, shopping, or handling sensitive information. 2. **Device Theft:** - High-traffic areas like security checkpoints, gates, and lounges are hotspots for device thefts. Always keep your devices in secure locations, such as carry-on bags or locked briefcases. 3. **Malware and Phishing Attacks:** - Some airports may have phishing attempts or malware distributed via pop-ups, email, or malicious websites. 4. **Physical Surveillance:** - In some cases, law enforcement or security personnel may monitor your activities. Always be mindful of your surroundings to avoid unintended data exposure. --- ### **Best Practices for Staying Digitally Safe in Airports** 1. **Use a VPN for Extra Security:** - Even secure airport Wi-Fi can expose your data if not encrypted. Use a reputable Virtual Private Network (VPN) to encrypt your internet traffic and protect your privacy. - Always ensure your VPN is active when using public Wi-Fi. 2. **Minimize Sensitive Data on Public Devices:** - Avoid carrying devices with sensitive information like passwords, credit card details, or personal identification numbers (PIIs). 3. **Encrypt Your Data:** - Enable encryption for all your devices to protect data stored locally or in the cloud. Ensure your operating system and apps are updated with the latest security patches. 4. **Secure Your Devices:** - Use cable locks or secure cases to lock down laptops, tablets, and smartphones when not in use. - Remove screensavers that display your device passcode to prevent unauthorized access. 5. **Keep Antivirus Software Updated:** - Install and maintain up-to-date antivirus software on all devices. This helps detect and remove malicious software (malware) that may be installed through compromised networks or phishing attempts. 6. **Avoid Plugging Into Public USB charging stations:** - Refrain from using public USB ports or charging stations unless you know they’re secure. Malware can spread via these points. 7. **Use Caution With Lost and Found:** - If you find a device or drop one accidentally, avoid using lost and found kiosks to pick it up. Instead, contact airport security for assistance in safely retrieving your property without exposing it to potential thieves. 8. **Stay Alert to Security Alerts:** - Pay attention to announcements over the airport’s PA system regarding suspicious activity or security alerts. Follow any instructions provided by airport staff. 9. **Monitor Your Accounts Remotely:** - If you suspect something is wrong (e.g., unusual transactions on your credit card), check your financial accounts immediately upon arriving at your destination. Notify your bank of potential fraudulent activity and report it to the authorities if necessary. --- ### **Additional Tips for Airport Safety** 1. **Use a Portable Power Bank:** - Keep your devices charged so you don’t rely on public charging stations, which may be compromised. 2. **Travel with Backup Devices:** - Always bring an extra SIM card, USB drive, or cloud storage to backup important data. This ensures you can access critical information even if your primary device is lost or damaged. 3. **Avoid Sharing Personal Information Over Earphone Rentals:** - Refrain from using earphones rented from airport kiosks that may record or intercept your conversations. Stick to your own headphones or those provided by the airline. 4. **Use Airport Lounges Wisely:** - If you’re using an airline lounge, avoid discussing sensitive information in public areas where it could be overheard. 5. **Keep Your Luggage in Sight:** - Never leave your checked luggage unattended, as it may contain devices or documents with sensitive information. 6. **Plan for Data Loss:** - Before leaving home, make a backup of all important files and photos on an external drive or cloud storage. This way, you can restore them if something goes wrong during your trip. --- ### **What to Do If Something Goes Wrong** 1. **Report Suspected Security Incidents:** - If you notice unusual activity on your devices or suspect a security breach, inform airport security immediately. 2. **Contact Your Financial Institutions:** - If you believe your financial information has been compromised, contact your bank or credit card provider to freeze your account and monitor for fraudulent charges. 3. **File a Police Report:** - In cases of theft or suspected unauthorized access, file a report with local authorities and provide evidence (if available). 4. **Use Travel Insurance:** - Check if your travel insurance covers theft, fraud, or data breaches. Submit a claim if you’re covered. --- ### **Extra Security Measures forTech-Savvy Travelers** - **Two-Factor Authentication (2FA):** Enable 2FA for all your critical accounts before leaving home. - **Biometric Locks:** Use biometric locks on your devices to add an extra layer of security. - **Incident Response Plan:** Create a plan in advance for what to do if your devices are lost or compromised. --- ### **Final Tips** - Always prioritize secure practices, even in seemingly safe environments like airports. - Travel light but keep your important documents and devices close at hand. - Remember that staying digitally safe is just as important as physical safety during your travels. By following these tips, you can enjoy your trip with peace of mind, knowing your data and devices are protected. Happy traveling! --- Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero 82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
@ 3b7fc823:e194354f
2025-02-12 23:13:57**Staying Digitally Safe in Airports: A Comprehensive Guide** Airports are hubs of activity, but they’re also places where your digital security can be at risk. From public Wi-Fi to potential device thefts, staying safe while traveling can feel overwhelming. However, with the right knowledge and precautions, you can protect yourself and enjoy your journey stress-free. Let’s dive into how to stay digitally safe in airports while traveling. --- ### **Understanding the Risks** 1. **Public Wi-Fi Vulnerabilities:** - Airports often offer free Wi-Fi, but these networks can be unsecured or insecure. Hackers may use these networks to intercept sensitive data. - Avoid using public Wi-Fi for personal banking, shopping, or handling sensitive information. 2. **Device Theft:** - High-traffic areas like security checkpoints, gates, and lounges are hotspots for device thefts. Always keep your devices in secure locations, such as carry-on bags or locked briefcases. 3. **Malware and Phishing Attacks:** - Some airports may have phishing attempts or malware distributed via pop-ups, email, or malicious websites. 4. **Physical Surveillance:** - In some cases, law enforcement or security personnel may monitor your activities. Always be mindful of your surroundings to avoid unintended data exposure. --- ### **Best Practices for Staying Digitally Safe in Airports** 1. **Use a VPN for Extra Security:** - Even secure airport Wi-Fi can expose your data if not encrypted. Use a reputable Virtual Private Network (VPN) to encrypt your internet traffic and protect your privacy. - Always ensure your VPN is active when using public Wi-Fi. 2. **Minimize Sensitive Data on Public Devices:** - Avoid carrying devices with sensitive information like passwords, credit card details, or personal identification numbers (PIIs). 3. **Encrypt Your Data:** - Enable encryption for all your devices to protect data stored locally or in the cloud. Ensure your operating system and apps are updated with the latest security patches. 4. **Secure Your Devices:** - Use cable locks or secure cases to lock down laptops, tablets, and smartphones when not in use. - Remove screensavers that display your device passcode to prevent unauthorized access. 5. **Keep Antivirus Software Updated:** - Install and maintain up-to-date antivirus software on all devices. This helps detect and remove malicious software (malware) that may be installed through compromised networks or phishing attempts. 6. **Avoid Plugging Into Public USB charging stations:** - Refrain from using public USB ports or charging stations unless you know they’re secure. Malware can spread via these points. 7. **Use Caution With Lost and Found:** - If you find a device or drop one accidentally, avoid using lost and found kiosks to pick it up. Instead, contact airport security for assistance in safely retrieving your property without exposing it to potential thieves. 8. **Stay Alert to Security Alerts:** - Pay attention to announcements over the airport’s PA system regarding suspicious activity or security alerts. Follow any instructions provided by airport staff. 9. **Monitor Your Accounts Remotely:** - If you suspect something is wrong (e.g., unusual transactions on your credit card), check your financial accounts immediately upon arriving at your destination. Notify your bank of potential fraudulent activity and report it to the authorities if necessary. --- ### **Additional Tips for Airport Safety** 1. **Use a Portable Power Bank:** - Keep your devices charged so you don’t rely on public charging stations, which may be compromised. 2. **Travel with Backup Devices:** - Always bring an extra SIM card, USB drive, or cloud storage to backup important data. This ensures you can access critical information even if your primary device is lost or damaged. 3. **Avoid Sharing Personal Information Over Earphone Rentals:** - Refrain from using earphones rented from airport kiosks that may record or intercept your conversations. Stick to your own headphones or those provided by the airline. 4. **Use Airport Lounges Wisely:** - If you’re using an airline lounge, avoid discussing sensitive information in public areas where it could be overheard. 5. **Keep Your Luggage in Sight:** - Never leave your checked luggage unattended, as it may contain devices or documents with sensitive information. 6. **Plan for Data Loss:** - Before leaving home, make a backup of all important files and photos on an external drive or cloud storage. This way, you can restore them if something goes wrong during your trip. --- ### **What to Do If Something Goes Wrong** 1. **Report Suspected Security Incidents:** - If you notice unusual activity on your devices or suspect a security breach, inform airport security immediately. 2. **Contact Your Financial Institutions:** - If you believe your financial information has been compromised, contact your bank or credit card provider to freeze your account and monitor for fraudulent charges. 3. **File a Police Report:** - In cases of theft or suspected unauthorized access, file a report with local authorities and provide evidence (if available). 4. **Use Travel Insurance:** - Check if your travel insurance covers theft, fraud, or data breaches. Submit a claim if you’re covered. --- ### **Extra Security Measures forTech-Savvy Travelers** - **Two-Factor Authentication (2FA):** Enable 2FA for all your critical accounts before leaving home. - **Biometric Locks:** Use biometric locks on your devices to add an extra layer of security. - **Incident Response Plan:** Create a plan in advance for what to do if your devices are lost or compromised. --- ### **Final Tips** - Always prioritize secure practices, even in seemingly safe environments like airports. - Travel light but keep your important documents and devices close at hand. - Remember that staying digitally safe is just as important as physical safety during your travels. By following these tips, you can enjoy your trip with peace of mind, knowing your data and devices are protected. Happy traveling! --- Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero 82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1 @ 000002de:c05780a7
2025-02-12 22:41:17The absolute embarrassment the Chiefs were subjected to... is the end of the their dominance? Of course they have a ton of talent and will win and maybe get back the Super Bowl this game really exposed them. Its one thing to lose to a great team like the Eagles. Its another to be destroyed so fully. When I think about this game its not just on one person. Its coaching and players. I'm just wondering about the impact on the league watching this. Anyone who has played sports knows that a ton of it is mental. Teams can defeat themselves mentally. Does this defeat tell the league, yeah they aren't that good. What do you think? Edit: When I say "done", I mean the dynasty. I don't mean they are gonna have a losing record next year. originally posted at https://stacker.news/items/884169
@ 000002de:c05780a7
2025-02-12 22:41:17The absolute embarrassment the Chiefs were subjected to... is the end of the their dominance? Of course they have a ton of talent and will win and maybe get back the Super Bowl this game really exposed them. Its one thing to lose to a great team like the Eagles. Its another to be destroyed so fully. When I think about this game its not just on one person. Its coaching and players. I'm just wondering about the impact on the league watching this. Anyone who has played sports knows that a ton of it is mental. Teams can defeat themselves mentally. Does this defeat tell the league, yeah they aren't that good. What do you think? Edit: When I say "done", I mean the dynasty. I don't mean they are gonna have a losing record next year. originally posted at https://stacker.news/items/884169 @ 000002de:c05780a7
2025-02-12 22:25:06Honest question. I think he's a great TE but... haven't watched him a ton. I get a feeling he's overrated. Maybe not though. I watched him during the big game and was kinda surprised by his lack luster performance. He really seemed different to me. Since then I've seen video of him not blocking for his QB and not really playing hard. Like he gave up. Does he really have a rep of not blocking? He looks pretty terrible on film. Now, I know I'm a Kittle fan and he is famously great at blocking and takes pride in it. Maybe I'm just using Kittle as the ruler and maybe that's not fair. Also, I loved watching KC get destroyed so factor that in :) originally posted at https://stacker.news/items/884156
@ 000002de:c05780a7
2025-02-12 22:25:06Honest question. I think he's a great TE but... haven't watched him a ton. I get a feeling he's overrated. Maybe not though. I watched him during the big game and was kinda surprised by his lack luster performance. He really seemed different to me. Since then I've seen video of him not blocking for his QB and not really playing hard. Like he gave up. Does he really have a rep of not blocking? He looks pretty terrible on film. Now, I know I'm a Kittle fan and he is famously great at blocking and takes pride in it. Maybe I'm just using Kittle as the ruler and maybe that's not fair. Also, I loved watching KC get destroyed so factor that in :) originally posted at https://stacker.news/items/884156 @ 37fe9853:bcd1b039
2025-01-11 15:04:40yoyoaa
@ 37fe9853:bcd1b039
2025-01-11 15:04:40yoyoaa @ 9673b322:1b75ee9e
2025-02-12 21:50:25This is my test document for nostr publish Although Sainsbury's was already in the midst of a plan to save £1bn over the next few years, the rise in employer's National Insurance contributions set out in the Budget has also been a factor in this latest restructuring plan. ### Add some text this is is a test 
@ 9673b322:1b75ee9e
2025-02-12 21:50:25This is my test document for nostr publish Although Sainsbury's was already in the midst of a plan to save £1bn over the next few years, the rise in employer's National Insurance contributions set out in the Budget has also been a factor in this latest restructuring plan. ### Add some text this is is a test  @ 5d4b6c8d:8a1c1ee3
2025-02-12 18:36:48Going off of memory, because I forgot to do this in the morning. The last thing I ate were Costco samples yesterday afternoon and then I didn't eat again until lunch today. I'm pretty sure those two things were about 20 hours apart. ## Score Card Day 1: 14 hour fast (13 dry) Day 2: 15 hour fast (14 dry) Day 3: 17 hours (16 dry) Day 4: 18 hours (17 dry) Day 5: 18 hours (16 dry) Day 6: 19 hours (16 dry) Day 7: 16 hours (15 dry) Day 8: 18 hours (17 dry) Day 9: 17 hours (17 dry) Day 10: 15 hours (13 dry) Day 11: 20 hours (19 dry) Day 12: 20 hours (17 dry) This winter storm is going to make getting my steps in a pain, but there's no way I'm letting myself lose the sats that I staked on the challenge. originally posted at https://stacker.news/items/884000
@ 5d4b6c8d:8a1c1ee3
2025-02-12 18:36:48Going off of memory, because I forgot to do this in the morning. The last thing I ate were Costco samples yesterday afternoon and then I didn't eat again until lunch today. I'm pretty sure those two things were about 20 hours apart. ## Score Card Day 1: 14 hour fast (13 dry) Day 2: 15 hour fast (14 dry) Day 3: 17 hours (16 dry) Day 4: 18 hours (17 dry) Day 5: 18 hours (16 dry) Day 6: 19 hours (16 dry) Day 7: 16 hours (15 dry) Day 8: 18 hours (17 dry) Day 9: 17 hours (17 dry) Day 10: 15 hours (13 dry) Day 11: 20 hours (19 dry) Day 12: 20 hours (17 dry) This winter storm is going to make getting my steps in a pain, but there's no way I'm letting myself lose the sats that I staked on the challenge. originally posted at https://stacker.news/items/884000 @ 2e8970de:63345c7a
2025-02-12 17:50:27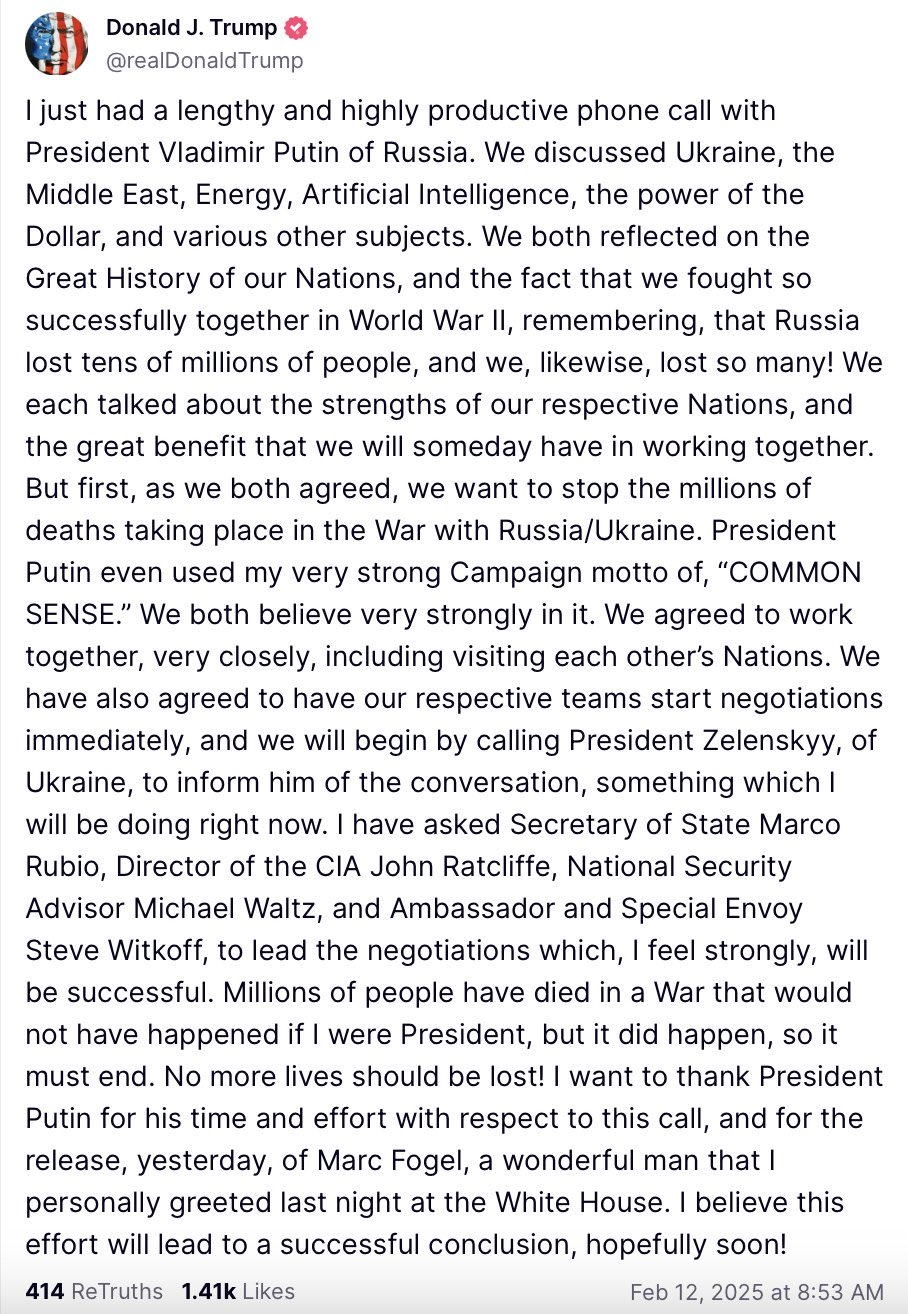 originally posted at https://stacker.news/items/883959
@ 2e8970de:63345c7a
2025-02-12 17:50:27 originally posted at https://stacker.news/items/883959 @ 62033ff8:e4471203
2025-01-11 15:00:24收录的内容中 kind=1的部分,实话说 质量不高。 所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。 所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。 而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。 https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。 我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。 我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛 幸运的是npub.pro 建站这样的,我觉得有点意思。 yakihonne 智能widget 也有意思 我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。
@ 62033ff8:e4471203
2025-01-11 15:00:24收录的内容中 kind=1的部分,实话说 质量不高。 所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。 所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。 而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。 https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。 我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。 我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛 幸运的是npub.pro 建站这样的,我觉得有点意思。 yakihonne 智能widget 也有意思 我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。 @ 4506e04e:8c16ba04
2025-01-10 13:26:46The healthcare system, in its current state, is fundamentally broken. Under the fiat standard, big pharma exploits the sick in much the same way that banks and financial corporations drain economic power from individuals and small businesses. Despite massive investments, healthcare remains plagued by inefficiencies, inequities, and vulnerabilities. With rapidly aging population and low birth rates the access to healthcare is becoming more and more difficult and the system will break within the next couple of decades. Here are some of the major issues: ### Financial Drain with Minimal Returns No matter how much money is poured into healthcare, it’s never enough. Administrative overheads, inflated costs, and inefficiencies ensure that resources are wasted instead of improving patient outcomes. ### Big Pharma’s Perverse Incentives Pharmaceutical companies prioritize profit over cures. The system is designed to keep patients alive but perpetually dependent on treatments, rather than focusing on true cures. ### Administrative Bloat The excessive overhead costs in administration siphon funds away from actual patient care. ### Fragmented Patient Records There is no single global standard for managing and accessing healthcare records, creating inefficiencies and potential for errors. ### Cybersecurity Risks Centralized healthcare systems are vulnerable to ransomware attacks, which can compromise patient safety and even pose threats to international security. For hospitals, such attacks are literally matters of life and death. ### Increasing Costs and Reduced Accessibility Instead of becoming cheaper and more accessible, healthcare is growing more expensive and difficult to obtain, exacerbating inequities, yet nurses are one of the groups that's most underpaid! ## A Decentralized Solution The solution lies in leveraging decentralization, encryption, and open-source technologies to transform the healthcare system. Thanks to innovations like Bitcoin and the Nostr protocol we now have the means to: - **Empower Patients and Doctors:** Decentralized systems can give patients control over their medical data while reducing administrative costs for healthcare providers. - **Enhance Security:** Encryption ensures data is secure, even in the face of cyber threats. - **Improve Accessibility and Efficiency:** Open-source tools (like [Keycast](https://github.com/erskingardner/keycast)) can lower costs and provide customizable solutions tailored to specific healthcare needs. note1327htu9gr327h38yu5f6tueye4cajp3kc69cs3gl7w6q6rz09ufqukl74j ## How Nostr Can Transform Healthcare Nostr, short for “*Notes and Other Stuff Transmitted by Relays,*” is a decentralized protocol originally designed for communication but holds tremendous potential for industries such as healthcare. Its client-relay model allows patients and doctors to interact securely without relying on centralized servers. Here’s how it could work in a healthcare context: ### Decentralized Data Control: Patients’ medical records can be securely stored and accessed via relays. Each patient’s identity is tied to a cryptographic public key, ensuring that they have full control over their data. Doctors can access necessary records by connecting to relays the patient authorizes, ensuring data remains private and secure. ### Privacy Without Bureaucracy: Nostr eliminates the need for cumbersome identity verification processes (e.g., KYC). Patients retain privacy without needing emails, IDs, or other personal identifiers. ### Customizable Access: Patients can specify which doctors or healthcare providers can access their records by granting permissions via cryptographic signatures. These permissions can be adjusted or revoked at any time. ### Secure and Verifiable Communication: All interactions between patients and doctors are signed with private keys, ensuring authenticity and preventing tampering. Relays do not own or manipulate the data; they simply transmit it between authorized users. ### Resilient and Flexible Network: Patients and doctors can choose which relays to use, and data can be published to multiple relays for redundancy. This ensures continuity of care even if a specific relay goes offline. ### Patient-Centric Data Ownership: In the Nostr model, patients own their data. They can share it, manage it, or restrict access as they see fit, empowering them to take control of their health information. ### Enhanced Telemedicine: Secure, encrypted communication enables remote consultations where doctors can access up-to-date patient records in real-time, providing better care. By combining Nostr’s decentralized approach with healthcare-specific adaptations, this protocol can make the healthcare system more secure, efficient, and patient-focused. ## Meet Keycast Keycast is a self-hosted open-source tool designed for secure and efficient private key management that can be applied to manage teams and policies. Its features can empower collaboration from micro-level ops like sharing access to one Nostr account to organising healthcare in the following ways: 1. **Team Management**: - Organize users into teams representing departments or specialties (different policies). - Streamline workflows by aligning permissions with roles. 2. **Granular Permissions**: - Assign specific access rights to doctors, nurses, and administrative staff. - Create layered permissions for actions such as accessing records, adding notes, or authorizing tests. 3. **Secure Key Management**: - Encrypt and securely store keys locally, ensuring data confidentiality. 4. **Remote Signing and Telemedicine**: - Enable secure remote access to records through NIP-46 for telehealth scenarios. 5. **Customizable Policies**: - Tailor permissions and content filters to suit healthcare needs, such as restricting access to certain records or anonymizing sensitive data. 6. **Patient Empowerment**: - Allow patients to manage access to their health information, promoting transparency and autonomy. ## Real-World Applications Here’s how these tools can address specific healthcare challenges: - **Secure Access to EHR:** Doctors and nurses can access patient records securely and efficiently, improving care coordination. - **AI-Driven Diagnostics:** AI agents with predefined, limited permissions can analyze data for diagnostics while safeguarding privacy. - **Telemedicine:** Secure, encrypted access ensures doctors can deliver remote care without compromising patient data. - **Anonymized Research:** Controlled access to anonymized data can accelerate medical research while protecting privacy. ## The Bigger Picture Decentralization is the key to fixing healthcare. Just like Bitcoin fixes the money and fixes the world - nostr and censorship-resistant encrypted data flow can fix whole industries like healthcare. By moving away from centralized, vulnerable systems, we can: 1. **Enhance Security:** Protect sensitive data from cyber threats with encryption and decentralized architectures. 2. **Lower Costs:** Reduce administrative overheads and eliminate inefficiencies. 3. **Improve Collaboration:** Foster better communication and coordination among healthcare professionals. 4. **Ensure Transparency:** Leverage open-source solutions to build trust and flexibility. ## Conclusion The healthcare systems we have today are heavily reliant on money printing. They are have turned into businesses with overgrown administrative layer. They are inefficient and unsustainable. However, by adopting the Nostr protocol and tools built upon it, we can create a system that is secure, efficient, and patient-centric. With open-source tools like these, healthcare can truly focused on improving lives, become cheaper, more accessible, and abundant. ### Challenge If you'd like to contribute to reinventing healthcare using free and open-source software built on the nostr protocol join the challenge by npub1healthsx3swcgtknff7zwpg8aj2q7h49zecul5rz490f6z2zp59qnfvp8p note1lnh3q6648ysulrx2pgeyhv2cqqle9vftdxalq3yqkqa7c89eljtqyr70nl
@ 4506e04e:8c16ba04
2025-01-10 13:26:46The healthcare system, in its current state, is fundamentally broken. Under the fiat standard, big pharma exploits the sick in much the same way that banks and financial corporations drain economic power from individuals and small businesses. Despite massive investments, healthcare remains plagued by inefficiencies, inequities, and vulnerabilities. With rapidly aging population and low birth rates the access to healthcare is becoming more and more difficult and the system will break within the next couple of decades. Here are some of the major issues: ### Financial Drain with Minimal Returns No matter how much money is poured into healthcare, it’s never enough. Administrative overheads, inflated costs, and inefficiencies ensure that resources are wasted instead of improving patient outcomes. ### Big Pharma’s Perverse Incentives Pharmaceutical companies prioritize profit over cures. The system is designed to keep patients alive but perpetually dependent on treatments, rather than focusing on true cures. ### Administrative Bloat The excessive overhead costs in administration siphon funds away from actual patient care. ### Fragmented Patient Records There is no single global standard for managing and accessing healthcare records, creating inefficiencies and potential for errors. ### Cybersecurity Risks Centralized healthcare systems are vulnerable to ransomware attacks, which can compromise patient safety and even pose threats to international security. For hospitals, such attacks are literally matters of life and death. ### Increasing Costs and Reduced Accessibility Instead of becoming cheaper and more accessible, healthcare is growing more expensive and difficult to obtain, exacerbating inequities, yet nurses are one of the groups that's most underpaid! ## A Decentralized Solution The solution lies in leveraging decentralization, encryption, and open-source technologies to transform the healthcare system. Thanks to innovations like Bitcoin and the Nostr protocol we now have the means to: - **Empower Patients and Doctors:** Decentralized systems can give patients control over their medical data while reducing administrative costs for healthcare providers. - **Enhance Security:** Encryption ensures data is secure, even in the face of cyber threats. - **Improve Accessibility and Efficiency:** Open-source tools (like [Keycast](https://github.com/erskingardner/keycast)) can lower costs and provide customizable solutions tailored to specific healthcare needs. note1327htu9gr327h38yu5f6tueye4cajp3kc69cs3gl7w6q6rz09ufqukl74j ## How Nostr Can Transform Healthcare Nostr, short for “*Notes and Other Stuff Transmitted by Relays,*” is a decentralized protocol originally designed for communication but holds tremendous potential for industries such as healthcare. Its client-relay model allows patients and doctors to interact securely without relying on centralized servers. Here’s how it could work in a healthcare context: ### Decentralized Data Control: Patients’ medical records can be securely stored and accessed via relays. Each patient’s identity is tied to a cryptographic public key, ensuring that they have full control over their data. Doctors can access necessary records by connecting to relays the patient authorizes, ensuring data remains private and secure. ### Privacy Without Bureaucracy: Nostr eliminates the need for cumbersome identity verification processes (e.g., KYC). Patients retain privacy without needing emails, IDs, or other personal identifiers. ### Customizable Access: Patients can specify which doctors or healthcare providers can access their records by granting permissions via cryptographic signatures. These permissions can be adjusted or revoked at any time. ### Secure and Verifiable Communication: All interactions between patients and doctors are signed with private keys, ensuring authenticity and preventing tampering. Relays do not own or manipulate the data; they simply transmit it between authorized users. ### Resilient and Flexible Network: Patients and doctors can choose which relays to use, and data can be published to multiple relays for redundancy. This ensures continuity of care even if a specific relay goes offline. ### Patient-Centric Data Ownership: In the Nostr model, patients own their data. They can share it, manage it, or restrict access as they see fit, empowering them to take control of their health information. ### Enhanced Telemedicine: Secure, encrypted communication enables remote consultations where doctors can access up-to-date patient records in real-time, providing better care. By combining Nostr’s decentralized approach with healthcare-specific adaptations, this protocol can make the healthcare system more secure, efficient, and patient-focused. ## Meet Keycast Keycast is a self-hosted open-source tool designed for secure and efficient private key management that can be applied to manage teams and policies. Its features can empower collaboration from micro-level ops like sharing access to one Nostr account to organising healthcare in the following ways: 1. **Team Management**: - Organize users into teams representing departments or specialties (different policies). - Streamline workflows by aligning permissions with roles. 2. **Granular Permissions**: - Assign specific access rights to doctors, nurses, and administrative staff. - Create layered permissions for actions such as accessing records, adding notes, or authorizing tests. 3. **Secure Key Management**: - Encrypt and securely store keys locally, ensuring data confidentiality. 4. **Remote Signing and Telemedicine**: - Enable secure remote access to records through NIP-46 for telehealth scenarios. 5. **Customizable Policies**: - Tailor permissions and content filters to suit healthcare needs, such as restricting access to certain records or anonymizing sensitive data. 6. **Patient Empowerment**: - Allow patients to manage access to their health information, promoting transparency and autonomy. ## Real-World Applications Here’s how these tools can address specific healthcare challenges: - **Secure Access to EHR:** Doctors and nurses can access patient records securely and efficiently, improving care coordination. - **AI-Driven Diagnostics:** AI agents with predefined, limited permissions can analyze data for diagnostics while safeguarding privacy. - **Telemedicine:** Secure, encrypted access ensures doctors can deliver remote care without compromising patient data. - **Anonymized Research:** Controlled access to anonymized data can accelerate medical research while protecting privacy. ## The Bigger Picture Decentralization is the key to fixing healthcare. Just like Bitcoin fixes the money and fixes the world - nostr and censorship-resistant encrypted data flow can fix whole industries like healthcare. By moving away from centralized, vulnerable systems, we can: 1. **Enhance Security:** Protect sensitive data from cyber threats with encryption and decentralized architectures. 2. **Lower Costs:** Reduce administrative overheads and eliminate inefficiencies. 3. **Improve Collaboration:** Foster better communication and coordination among healthcare professionals. 4. **Ensure Transparency:** Leverage open-source solutions to build trust and flexibility. ## Conclusion The healthcare systems we have today are heavily reliant on money printing. They are have turned into businesses with overgrown administrative layer. They are inefficient and unsustainable. However, by adopting the Nostr protocol and tools built upon it, we can create a system that is secure, efficient, and patient-centric. With open-source tools like these, healthcare can truly focused on improving lives, become cheaper, more accessible, and abundant. ### Challenge If you'd like to contribute to reinventing healthcare using free and open-source software built on the nostr protocol join the challenge by npub1healthsx3swcgtknff7zwpg8aj2q7h49zecul5rz490f6z2zp59qnfvp8p note1lnh3q6648ysulrx2pgeyhv2cqqle9vftdxalq3yqkqa7c89eljtqyr70nl @ f3df9bc0:a95119eb
2025-01-10 02:58:08# MPT Equations ### Geometric Mean $$ \bar{x} = (\prod_{i=1}^{n} x_i)^{1 \over n } $$ ### Covariance $$ COV(x,y) = {1\over{n-1}} \sum_{i=1}^{n}{(x_i - \bar{x})(y_i - \bar{y})} $$ where $\bar{x}$ and $\bar{y}$ are the **geometric** mean. ### Variance $$ VAR(x) = {1\over{n-1}} \sum_{i=1}^{n}{(x_i - \bar{x})^2} $$ ### Standard Deviation $$ \sigma_x=\sqrt{VAR(x)} $$ ### Correlation Coefficient $$ \rho_{xy} = {COV(x, y) \over \sigma_x\sigma_y} $$ ### Portfolio Variance $$ VAR(P) = \sum_{ij}w_i w_j COV(i, j) $$ Where $w_i$ and $w_j$ are the normalized weight of the asset in the portfolio. Note that this summation should include when $i = j$. In this case $COV(i, j) = VAR(i) = VAR(j)$ ### Expected Return $$ E_P = \sum_{i}w_i E_i $$ Where $w_i$ is the normalized weight of the asset, and $E_i$ is the expected return of the individual asset.
@ f3df9bc0:a95119eb
2025-01-10 02:58:08# MPT Equations ### Geometric Mean $$ \bar{x} = (\prod_{i=1}^{n} x_i)^{1 \over n } $$ ### Covariance $$ COV(x,y) = {1\over{n-1}} \sum_{i=1}^{n}{(x_i - \bar{x})(y_i - \bar{y})} $$ where $\bar{x}$ and $\bar{y}$ are the **geometric** mean. ### Variance $$ VAR(x) = {1\over{n-1}} \sum_{i=1}^{n}{(x_i - \bar{x})^2} $$ ### Standard Deviation $$ \sigma_x=\sqrt{VAR(x)} $$ ### Correlation Coefficient $$ \rho_{xy} = {COV(x, y) \over \sigma_x\sigma_y} $$ ### Portfolio Variance $$ VAR(P) = \sum_{ij}w_i w_j COV(i, j) $$ Where $w_i$ and $w_j$ are the normalized weight of the asset in the portfolio. Note that this summation should include when $i = j$. In this case $COV(i, j) = VAR(i) = VAR(j)$ ### Expected Return $$ E_P = \sum_{i}w_i E_i $$ Where $w_i$ is the normalized weight of the asset, and $E_i$ is the expected return of the individual asset. @ 8d34bd24:414be32b
2025-02-12 17:38:19All of us who have truly put our faith in the Lord Jesus Christ want to serve Him, but we all live busy lives. We all get distracted by making a living, taking care of our families, and other good things, but too often we spend so much time on the good that we miss out on the best (see “[Don’t Be Like Martha](https://trustjesus.substack.com/p/dont-be-like-martha)”). In this previous post, I wrote about how we don’t want to live. In this post, I’ll write about what the Bible says about living a life wholly devoted to God. Many of us wonder, “Are we fully serving God if we aren’t in full time ministry, if we aren’t a pastor/priest, missionary, or if we don’t work for a Christian ministry?” There are many ways we can serve God. Sometimes we are called to a Christian “job,” but other times we serve God in other ways. > Let the word of Christ richly dwell within you, with all wisdom teaching and admonishing one another with psalms and hymns and spiritual songs, singing with thankfulness in your hearts to God. **Whatever you do in word or deed, do all in the name of the Lord Jesus, giving thanks through Him to God the Father**. (Colossians 3:16-17) {emphasis mine} The most important thing is that everything we do has a godly focus. We should follow God’s design for marriage and family. We should disciple our children to know and grow in Jesus. We should witness to those with whom we come in contact. We should give to support those who are working in full-time ministry. Even our jobs can be done in service to the Lord, no matter how trivial or unrelated that job might seem. > **Whatever you do, do your work heartily, as for the Lord rather than for men**, knowing that from the Lord you will receive the reward of the inheritance. It is the Lord Christ whom you serve. (Colossians 3:23-24) {emphasis mine} I’m an employer. I see the work ethic, or more often the lack of work ethic, in people. I notice those who work hard and always give their best versus those who do the minimum they need to do to keep their job. When a person lets everyone around them know that they are a Christian and then they work harder than everyone else and they are willing to do the undesirable tasks that need to be done, this is noticed and is a good witness. Sadly, too often Christians are known for not working as hard and not going the extra mile. These Christians give Jesus and all Christians a bad name. Whatever job God has given you, do it to the best of your ability. Do the extra task; do the undesirable task; do the task that should’ve been done by someone else. Put in the extra effort even if nobody seems to notice. In most case, even if you aren’t praised, appreciated, or appropriately rewarded, people do notice and your witness is enhanced. In all cases, Jesus notices and you will be rewarded in heaven for representing Him faithfully. > Whether, then, you eat or drink or whatever you do, **do all to the glory of God**. (1 Corinthians 10:31) {emphasis mine} We are to do everything we do to the God’s glory. The way we work should glorify God. The way we eat and drink should glorify God. The way we do rest and entertainment should glorify God. The way we interact with others should glorify God. We were designed to glorify God. Too often we get busy doing life and leave God out of it. It isn’t that we are doing some terrible sin, but it is always wrong to leave God out of our life. We can even do Christian ministry and get so busy doing “God’s work” that we leave God out of it. This can be disastrous and definitely will damage ministry effectiveness. In everything we do, we should listen to God’s leading, whether through Bible reading, prayer, or being still and listening. > The plans of the heart belong to man,\ > But the answer of the tongue is from the Lord.\ > All the ways of a man are clean in his own sight,\ > But the Lord weighs the motives.\ ****Commit your works to the Lord\ > And your plans will be established**. (Proverbs 16:1-3) {emphasis mine} Part of doing everything in and to the Lord is changing our hearts and minds. Psalm 37 lists several actions we can take in serving the Lord and becoming more like Him. > **Delight yourself in the Lord**;\ > And He will give you the desires of your heart.\ ****Commit your way to the Lord**,\ ****Trust also in Him**, and He will do it.\ > He will bring forth your righteousness as the light\ > And your judgment as the noonday.\ ****Rest in the Lord and wait patiently for Him**;\ ****Do not fret** because of him who prospers in his way,\ > Because of the man who carries out wicked schemes.\ ****Cease from anger and forsake wrath**;\ > Do not fret; it leads only to evildoing. (Psalm 37:4-8) {emphasis mine} If we delight in the Lord, commit our way to the Lord, trust in Him, rest in the Lord, and wait patiently for the Lord, we will be in the right mind to serve Him in all that we do. It will also help us avoid the things that draw us away from the Lord. We are called to not fret, to cease from anger, and to forsake wrath. Fretting, anger, and wrath hurt our witness and draw us away from God. They are a sign that our hearts are not in tune with God and that we need to turn back to Him. They are a sign that we are not trusting in Him nor are we following His will. --- Sometimes believers wonder if they are succeeding in doing anything for the Lord because they are shy and not good at witnessing or because they have personal circumstances (like sickness of themselves or their family members) that don’t allow them to do much. That doesn’t mean there is nothing these believers can do. We can support those doing the mission of God. We can give money to support missionaries, churches, and Christian ministries. We can house a missionary while they are on break. We can do behind the scenes tasks like cleaning, accounting, organizing, planning, etc. Most importantly, we can all pray. Prayer should be a constant part of every day, whether we are infirm and unable to leave our bed, whether we are so busy we don’t have five minutes to sit and take a break, or whether we are in full time Christian ministry. We can’t faithfully serve God without prayer. > Beloved, **you are acting faithfully in whatever you accomplish for the brethren**, and especially *when they are* strangers; and they have testified to your love before the church. You will do well to send them on their way in a manner worthy of God. For they went out for the sake of the Name, accepting nothing from the Gentiles. Therefore **we ought to support such men, so that we may be fellow workers with the truth**. (3 John 1:5-8) {emphasis mine} Anyone who supports those in ministry will receive similar rewards to those in ministry because they are all working together to fulfill God’s will. > He who receives a prophet in the name of a prophet shall receive a prophet’s reward; and he who receives a righteous man in the name of a righteous man shall receive a righteous man’s reward. (Matthew 10:41) We often feel like we are failing God. We feel that we are making zero difference for the kingdom. If you are not growing in your faith, knowledge, and relationship with God, there may be some truth in this, but we also may be listening to the accuser, Satan. Keep in mind that every little thing you do for Jesus or for others, because of your faith in Jesus, is counted as faithful service to Him. > “Then the King will say to those on His right, ‘Come, you who are blessed of My Father, inherit the kingdom prepared for you from the foundation of the world. For I was hungry, and you gave Me something to eat; I was thirsty, and you gave Me something to drink; I was a stranger, and you invited Me in; naked, and you clothed Me; I was sick, and you visited Me; I was in prison, and you came to Me.’ Then the righteous will answer Him, ‘Lord, when did we see You hungry, and feed You, or thirsty, and give You something to drink? And when did we see You a stranger, and invite You in, or naked, and clothe You? When did we see You sick, or in prison, and come to You?’ The King will answer and say to them, ‘**Truly I say to you, to the extent that you did it to one of these brothers of Mine, even the least of them, you did it to Me**.’ (Matthew 25:34-40) {emphasis mine} Turn to Jesus. Pray to Jesus. Read His word —the Bible. Make Him a part of everything you do. Follow His leading. Join God in what He is doing. May God bless you and lead you in the path He designed you to take. Trust Jesus.
@ 8d34bd24:414be32b
2025-02-12 17:38:19All of us who have truly put our faith in the Lord Jesus Christ want to serve Him, but we all live busy lives. We all get distracted by making a living, taking care of our families, and other good things, but too often we spend so much time on the good that we miss out on the best (see “[Don’t Be Like Martha](https://trustjesus.substack.com/p/dont-be-like-martha)”). In this previous post, I wrote about how we don’t want to live. In this post, I’ll write about what the Bible says about living a life wholly devoted to God. Many of us wonder, “Are we fully serving God if we aren’t in full time ministry, if we aren’t a pastor/priest, missionary, or if we don’t work for a Christian ministry?” There are many ways we can serve God. Sometimes we are called to a Christian “job,” but other times we serve God in other ways. > Let the word of Christ richly dwell within you, with all wisdom teaching and admonishing one another with psalms and hymns and spiritual songs, singing with thankfulness in your hearts to God. **Whatever you do in word or deed, do all in the name of the Lord Jesus, giving thanks through Him to God the Father**. (Colossians 3:16-17) {emphasis mine} The most important thing is that everything we do has a godly focus. We should follow God’s design for marriage and family. We should disciple our children to know and grow in Jesus. We should witness to those with whom we come in contact. We should give to support those who are working in full-time ministry. Even our jobs can be done in service to the Lord, no matter how trivial or unrelated that job might seem. > **Whatever you do, do your work heartily, as for the Lord rather than for men**, knowing that from the Lord you will receive the reward of the inheritance. It is the Lord Christ whom you serve. (Colossians 3:23-24) {emphasis mine} I’m an employer. I see the work ethic, or more often the lack of work ethic, in people. I notice those who work hard and always give their best versus those who do the minimum they need to do to keep their job. When a person lets everyone around them know that they are a Christian and then they work harder than everyone else and they are willing to do the undesirable tasks that need to be done, this is noticed and is a good witness. Sadly, too often Christians are known for not working as hard and not going the extra mile. These Christians give Jesus and all Christians a bad name. Whatever job God has given you, do it to the best of your ability. Do the extra task; do the undesirable task; do the task that should’ve been done by someone else. Put in the extra effort even if nobody seems to notice. In most case, even if you aren’t praised, appreciated, or appropriately rewarded, people do notice and your witness is enhanced. In all cases, Jesus notices and you will be rewarded in heaven for representing Him faithfully. > Whether, then, you eat or drink or whatever you do, **do all to the glory of God**. (1 Corinthians 10:31) {emphasis mine} We are to do everything we do to the God’s glory. The way we work should glorify God. The way we eat and drink should glorify God. The way we do rest and entertainment should glorify God. The way we interact with others should glorify God. We were designed to glorify God. Too often we get busy doing life and leave God out of it. It isn’t that we are doing some terrible sin, but it is always wrong to leave God out of our life. We can even do Christian ministry and get so busy doing “God’s work” that we leave God out of it. This can be disastrous and definitely will damage ministry effectiveness. In everything we do, we should listen to God’s leading, whether through Bible reading, prayer, or being still and listening. > The plans of the heart belong to man,\ > But the answer of the tongue is from the Lord.\ > All the ways of a man are clean in his own sight,\ > But the Lord weighs the motives.\ ****Commit your works to the Lord\ > And your plans will be established**. (Proverbs 16:1-3) {emphasis mine} Part of doing everything in and to the Lord is changing our hearts and minds. Psalm 37 lists several actions we can take in serving the Lord and becoming more like Him. > **Delight yourself in the Lord**;\ > And He will give you the desires of your heart.\ ****Commit your way to the Lord**,\ ****Trust also in Him**, and He will do it.\ > He will bring forth your righteousness as the light\ > And your judgment as the noonday.\ ****Rest in the Lord and wait patiently for Him**;\ ****Do not fret** because of him who prospers in his way,\ > Because of the man who carries out wicked schemes.\ ****Cease from anger and forsake wrath**;\ > Do not fret; it leads only to evildoing. (Psalm 37:4-8) {emphasis mine} If we delight in the Lord, commit our way to the Lord, trust in Him, rest in the Lord, and wait patiently for the Lord, we will be in the right mind to serve Him in all that we do. It will also help us avoid the things that draw us away from the Lord. We are called to not fret, to cease from anger, and to forsake wrath. Fretting, anger, and wrath hurt our witness and draw us away from God. They are a sign that our hearts are not in tune with God and that we need to turn back to Him. They are a sign that we are not trusting in Him nor are we following His will. --- Sometimes believers wonder if they are succeeding in doing anything for the Lord because they are shy and not good at witnessing or because they have personal circumstances (like sickness of themselves or their family members) that don’t allow them to do much. That doesn’t mean there is nothing these believers can do. We can support those doing the mission of God. We can give money to support missionaries, churches, and Christian ministries. We can house a missionary while they are on break. We can do behind the scenes tasks like cleaning, accounting, organizing, planning, etc. Most importantly, we can all pray. Prayer should be a constant part of every day, whether we are infirm and unable to leave our bed, whether we are so busy we don’t have five minutes to sit and take a break, or whether we are in full time Christian ministry. We can’t faithfully serve God without prayer. > Beloved, **you are acting faithfully in whatever you accomplish for the brethren**, and especially *when they are* strangers; and they have testified to your love before the church. You will do well to send them on their way in a manner worthy of God. For they went out for the sake of the Name, accepting nothing from the Gentiles. Therefore **we ought to support such men, so that we may be fellow workers with the truth**. (3 John 1:5-8) {emphasis mine} Anyone who supports those in ministry will receive similar rewards to those in ministry because they are all working together to fulfill God’s will. > He who receives a prophet in the name of a prophet shall receive a prophet’s reward; and he who receives a righteous man in the name of a righteous man shall receive a righteous man’s reward. (Matthew 10:41) We often feel like we are failing God. We feel that we are making zero difference for the kingdom. If you are not growing in your faith, knowledge, and relationship with God, there may be some truth in this, but we also may be listening to the accuser, Satan. Keep in mind that every little thing you do for Jesus or for others, because of your faith in Jesus, is counted as faithful service to Him. > “Then the King will say to those on His right, ‘Come, you who are blessed of My Father, inherit the kingdom prepared for you from the foundation of the world. For I was hungry, and you gave Me something to eat; I was thirsty, and you gave Me something to drink; I was a stranger, and you invited Me in; naked, and you clothed Me; I was sick, and you visited Me; I was in prison, and you came to Me.’ Then the righteous will answer Him, ‘Lord, when did we see You hungry, and feed You, or thirsty, and give You something to drink? And when did we see You a stranger, and invite You in, or naked, and clothe You? When did we see You sick, or in prison, and come to You?’ The King will answer and say to them, ‘**Truly I say to you, to the extent that you did it to one of these brothers of Mine, even the least of them, you did it to Me**.’ (Matthew 25:34-40) {emphasis mine} Turn to Jesus. Pray to Jesus. Read His word —the Bible. Make Him a part of everything you do. Follow His leading. Join God in what He is doing. May God bless you and lead you in the path He designed you to take. Trust Jesus. @ dd664d5e:5633d319
2025-01-09 21:39:15# Instructions 1. Place 2 medium-sized, boiled potatoes and a handful of sliced leeks in a pot.  2. Fill the pot with water or vegetable broth, to cover the potatoes twice over. 3. Add a splash of white wine, if you like, and some bouillon powder, if you went with water instead of broth.  4. Bring the soup to a boil and then simmer for 15 minutes. 5. Puree the soup, in the pot, with a hand mixer. It shouldn't be completely smooth, when you're done, but rather have small bits and pieces of the veggies floating around.  6. Bring the soup to a boil, again, and stir in one container (200-250 mL) of heavy cream. 7. Thicken the soup, as needed, and then simmer for 5 more minutes. 8. Garnish with croutons and veggies (here I used sliced green onions and radishes) and serve.  Guten Appetit!
@ dd664d5e:5633d319
2025-01-09 21:39:15# Instructions 1. Place 2 medium-sized, boiled potatoes and a handful of sliced leeks in a pot.  2. Fill the pot with water or vegetable broth, to cover the potatoes twice over. 3. Add a splash of white wine, if you like, and some bouillon powder, if you went with water instead of broth.  4. Bring the soup to a boil and then simmer for 15 minutes. 5. Puree the soup, in the pot, with a hand mixer. It shouldn't be completely smooth, when you're done, but rather have small bits and pieces of the veggies floating around.  6. Bring the soup to a boil, again, and stir in one container (200-250 mL) of heavy cream. 7. Thicken the soup, as needed, and then simmer for 5 more minutes. 8. Garnish with croutons and veggies (here I used sliced green onions and radishes) and serve.  Guten Appetit! @ 88cc134b:5ae99079
2025-02-12 17:23:02aaaaaa
@ 88cc134b:5ae99079
2025-02-12 17:23:02aaaaaa @ d61f3bc5:0da6ef4a
2025-02-12 16:57:44Micropayments on the Internet have been theorized for decades. However, it wasn’t until the emergence of Nostr that we’ve finally seen them deployed at scale. Nostr is still in its infancy, yet we are already witnessing an explosion of apps built on top of this open protocol. And most of them are featuring zaps! With the recent Primal 2.1 release, Nostr developers now have the option to enhance the experience for their users by integrating a Nostr-powered bitcoin wallet. There is no doubt that micropayments add a new dimension to consumer apps. The incumbents have realized this and are rushing to add payments to their closed platforms. It won't be long before apps that don’t include built-in payments feel dated or outright broken. The question is not if apps of the future will have built-in payments, but what *kind* of payments they will be. Given that open networks have a tendency to win, our bet is that apps of the future will be powered by Bitcoin. Let’s see how Primal can help. ## Primal Wallet Our vision for Primal Wallet is simple: deliver the smoothest transactional bitcoin wallet, endowed with expert Nostr skills. The wallet leverages Nostr’s open social graph as a de facto public lightning directory, while offering the highest level of user experience for Nostr’s rich content. For example, the user can scroll through the transaction list, select a zap, and drill straight into the conversation thread where the zap originated. The whole flow feels perfectly natural.  Since we launched Primal Wallet in December 2023, the user response has been incredibly positive. People love the idea of being able to post something on Nostr, get zaps from plebs around the world, then buy a coffee or a meal with those sats - all from the same app. Having a bitcoin wallet with social skills resonated strongly with users, so Primal Wallet grew rapidly in popularity and usage. Since the launch, we have processed **1,338,460** transactions, with **238,916** just in the past month alone. This rivals some of the leading bitcoin wallets, and we are just getting started! We hear from many bitcoin OGs that they are using Primal Wallet as their transactional daily driver. Bullish. All this is great, but something has been missing. Our users demanded the ability to connect Primal Wallet to other Nostr apps, so they can zap from anywhere in Nostr’s growing ecosystem. ## Zapping from Any Nostr App For an existing Primal user, connecting the wallet to a new Nostr app can now be done in two clicks. Let’s take a look at how this is done from Olas, one of the most exciting new apps on Nostr:  Yes. Click, click. And you can start zapping! Such smooth integration of payments is not available in any competing technology stack. Tradfi, fintech, crypto, etc., have nothing on Bitcoin and Nostr. Two clicks and your external wallet is connected. I’ll give you a moment now to allow for this new reality to settle in. Primal enables you to connect any number of external apps and manage them from wallet settings:  Note that you can set your daily spend budget for each app or revoke its access at any time. ## How This Works So, what is this sorcery? How does it work under the hood? Connecting Nostr apps to external wallets is accomplished via the Nostr Wallet Connect protocol. It utilizes Nostr’s public relay infrastructure to enable communication between apps and wallets. You can learn more about this protocol [here](https://nwc.dev/), and access developer docs [here](https://docs.nwc.dev/). The smooth, two-click connection setup UX is implemented through deep links between Primal and the external app. Here’s the deep link that the external app needs to call to invoke this feature: ```nostrnwc+primal://connect?appicon=[icon_url]&appname=[app_name]&callback=[callback_string]``` After the user clicks “Create Wallet Connection” in Primal, the Primal app calls the deep link defined in the callback, and passes the NWC connection string. That's all that the external app needs to make the wallet connection. ## What Comes Next? The Nostr Wallet Connect protocol has been around for almost two years. Several bitcoin wallets implement it and many Nostr apps use it as their main way of enabling payments. What’s new with Primal 2.1 is the elevated user experience. Since Primal is a Nostr-powered wallet, it is aware of all the relevant metadata for each transaction: Nostr zaps, users, and the related events. Primal indexes the entire Nostr network, and now this is open to all Nostr apps that wish to integrate payments. Nostr keeps expanding and getting better. Its openness enables us to build capabilities that lift all boats. The future is bright; I can’t wait to see how things evolve from here. 🍿🍿🍿
@ d61f3bc5:0da6ef4a
2025-02-12 16:57:44Micropayments on the Internet have been theorized for decades. However, it wasn’t until the emergence of Nostr that we’ve finally seen them deployed at scale. Nostr is still in its infancy, yet we are already witnessing an explosion of apps built on top of this open protocol. And most of them are featuring zaps! With the recent Primal 2.1 release, Nostr developers now have the option to enhance the experience for their users by integrating a Nostr-powered bitcoin wallet. There is no doubt that micropayments add a new dimension to consumer apps. The incumbents have realized this and are rushing to add payments to their closed platforms. It won't be long before apps that don’t include built-in payments feel dated or outright broken. The question is not if apps of the future will have built-in payments, but what *kind* of payments they will be. Given that open networks have a tendency to win, our bet is that apps of the future will be powered by Bitcoin. Let’s see how Primal can help. ## Primal Wallet Our vision for Primal Wallet is simple: deliver the smoothest transactional bitcoin wallet, endowed with expert Nostr skills. The wallet leverages Nostr’s open social graph as a de facto public lightning directory, while offering the highest level of user experience for Nostr’s rich content. For example, the user can scroll through the transaction list, select a zap, and drill straight into the conversation thread where the zap originated. The whole flow feels perfectly natural.  Since we launched Primal Wallet in December 2023, the user response has been incredibly positive. People love the idea of being able to post something on Nostr, get zaps from plebs around the world, then buy a coffee or a meal with those sats - all from the same app. Having a bitcoin wallet with social skills resonated strongly with users, so Primal Wallet grew rapidly in popularity and usage. Since the launch, we have processed **1,338,460** transactions, with **238,916** just in the past month alone. This rivals some of the leading bitcoin wallets, and we are just getting started! We hear from many bitcoin OGs that they are using Primal Wallet as their transactional daily driver. Bullish. All this is great, but something has been missing. Our users demanded the ability to connect Primal Wallet to other Nostr apps, so they can zap from anywhere in Nostr’s growing ecosystem. ## Zapping from Any Nostr App For an existing Primal user, connecting the wallet to a new Nostr app can now be done in two clicks. Let’s take a look at how this is done from Olas, one of the most exciting new apps on Nostr:  Yes. Click, click. And you can start zapping! Such smooth integration of payments is not available in any competing technology stack. Tradfi, fintech, crypto, etc., have nothing on Bitcoin and Nostr. Two clicks and your external wallet is connected. I’ll give you a moment now to allow for this new reality to settle in. Primal enables you to connect any number of external apps and manage them from wallet settings:  Note that you can set your daily spend budget for each app or revoke its access at any time. ## How This Works So, what is this sorcery? How does it work under the hood? Connecting Nostr apps to external wallets is accomplished via the Nostr Wallet Connect protocol. It utilizes Nostr’s public relay infrastructure to enable communication between apps and wallets. You can learn more about this protocol [here](https://nwc.dev/), and access developer docs [here](https://docs.nwc.dev/). The smooth, two-click connection setup UX is implemented through deep links between Primal and the external app. Here’s the deep link that the external app needs to call to invoke this feature: ```nostrnwc+primal://connect?appicon=[icon_url]&appname=[app_name]&callback=[callback_string]``` After the user clicks “Create Wallet Connection” in Primal, the Primal app calls the deep link defined in the callback, and passes the NWC connection string. That's all that the external app needs to make the wallet connection. ## What Comes Next? The Nostr Wallet Connect protocol has been around for almost two years. Several bitcoin wallets implement it and many Nostr apps use it as their main way of enabling payments. What’s new with Primal 2.1 is the elevated user experience. Since Primal is a Nostr-powered wallet, it is aware of all the relevant metadata for each transaction: Nostr zaps, users, and the related events. Primal indexes the entire Nostr network, and now this is open to all Nostr apps that wish to integrate payments. Nostr keeps expanding and getting better. Its openness enables us to build capabilities that lift all boats. The future is bright; I can’t wait to see how things evolve from here. 🍿🍿🍿 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52## **Necessário** - Um Android que você não use mais (a câmera deve estar funcionando). - Um cartão microSD (opcional, usado apenas uma vez). - Um dispositivo para acompanhar seus fundos (provavelmente você já tem um). ## **Algumas coisas que você precisa saber** - O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele. - O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito. - A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal. --- ## **O tutorial será dividido em dois módulos:** - Módulo 1 - Criando uma carteira fria/assinador. - Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador. --- ## **No final, teremos:** - Uma carteira fria que também servirá como assinador. - Um dispositivo para acompanhar os fundos da carteira.  --- ## **Módulo 1 - Criando uma carteira fria/assinador** 1. Baixe o APK do Electrum na aba de **downloads** em <https://electrum.org/>. Fique à vontade para [verificar as assinaturas](https://electrum.readthedocs.io/en/latest/gpg-check.html) do software, garantindo sua autenticidade. 2. Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.  3. Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.  4. Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o **modo avião**.\ *(Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)*  5. Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.  6. No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. *(Aqui entra seu método pessoal de backup.)*  --- ## **Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.** 1. Criar uma carteira **somente leitura** em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em <https://electrum.org/> ou da própria Play Store. *(ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)* 2. Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção **Usar uma chave mestra**.  3. Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em **Carteira > Detalhes da carteira > Compartilhar chave mestra pública**.  4. Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los. 5. Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: **Carteira > Addresses/Coins**. 6. Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.  7. No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.  8. No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede. --- ## **Conclusão** **Pontos positivos do setup:** - **Simplicidade:** Basta um dispositivo Android antigo. - **Flexibilidade:** Funciona como uma ótima carteira fria, ideal para holders. **Pontos negativos do setup:** - **Padronização:** Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum. - **Interface:** A aparência do Electrum pode parecer antiquada para alguns usuários. Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: ***Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.*** Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível. ---
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52## **Necessário** - Um Android que você não use mais (a câmera deve estar funcionando). - Um cartão microSD (opcional, usado apenas uma vez). - Um dispositivo para acompanhar seus fundos (provavelmente você já tem um). ## **Algumas coisas que você precisa saber** - O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele. - O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito. - A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal. --- ## **O tutorial será dividido em dois módulos:** - Módulo 1 - Criando uma carteira fria/assinador. - Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador. --- ## **No final, teremos:** - Uma carteira fria que também servirá como assinador. - Um dispositivo para acompanhar os fundos da carteira.  --- ## **Módulo 1 - Criando uma carteira fria/assinador** 1. Baixe o APK do Electrum na aba de **downloads** em <https://electrum.org/>. Fique à vontade para [verificar as assinaturas](https://electrum.readthedocs.io/en/latest/gpg-check.html) do software, garantindo sua autenticidade. 2. Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.  3. Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.  4. Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o **modo avião**.\ *(Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)*  5. Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.  6. No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. *(Aqui entra seu método pessoal de backup.)*  --- ## **Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.** 1. Criar uma carteira **somente leitura** em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em <https://electrum.org/> ou da própria Play Store. *(ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)* 2. Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção **Usar uma chave mestra**.  3. Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em **Carteira > Detalhes da carteira > Compartilhar chave mestra pública**.  4. Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los. 5. Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: **Carteira > Addresses/Coins**. 6. Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.  7. No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.  8. No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede. --- ## **Conclusão** **Pontos positivos do setup:** - **Simplicidade:** Basta um dispositivo Android antigo. - **Flexibilidade:** Funciona como uma ótima carteira fria, ideal para holders. **Pontos negativos do setup:** - **Padronização:** Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum. - **Interface:** A aparência do Electrum pode parecer antiquada para alguns usuários. Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: ***Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.*** Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível. --- @ 85bdb587:7339d672
2025-02-12 15:24:11## Chart of the Day While this is a bitcoin focused rag, I think it is important for any of you who read this to begin paying attention to gold markets if you haven't already. There has been an ongoing exodus of physical gold from London vaults and a rapid acceleration of gold being moved to the three biggest vaults in the United States in recent weeks. More gold has flooded into the US vaults over the first two months of this year than at the peak of the flight to safety during the beginning of the COVID lock downs. 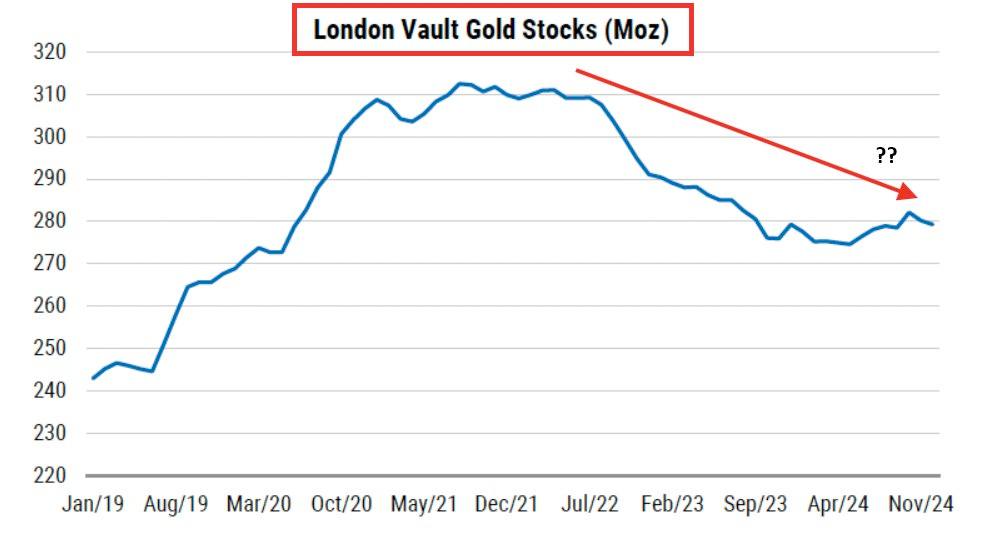 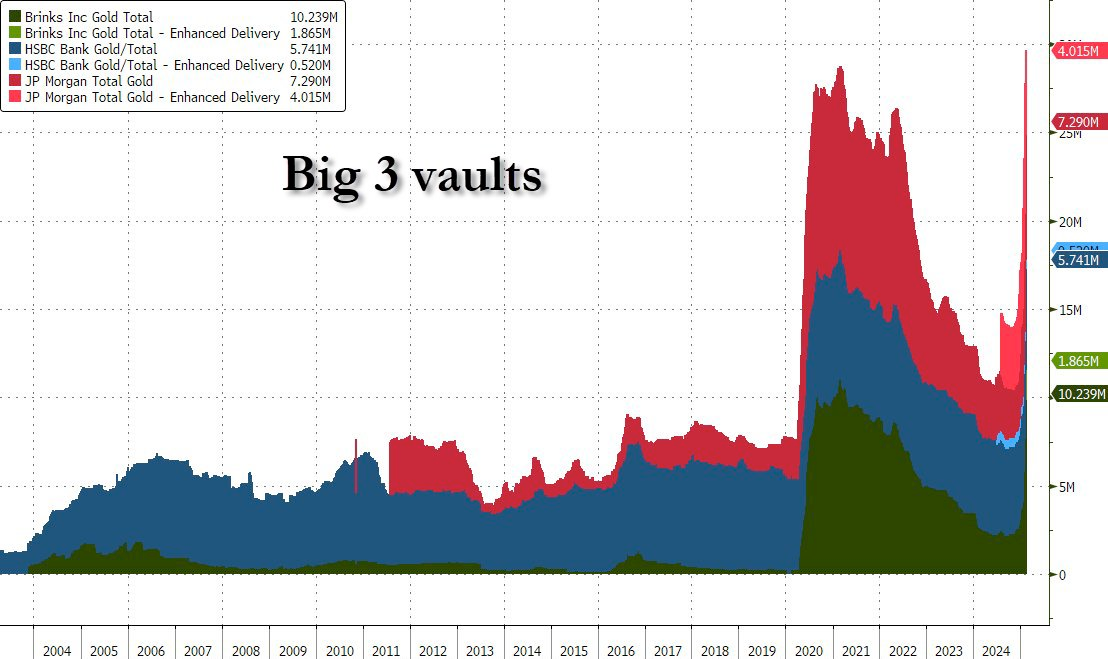 This is particularly perplexing considering the fact that equities are flat or up on the year, depending on the index you like to follow. Gold outperformed the S&P 500 significantly in 2024 and its momentum hasn't slowed down a bit in 2025 as the precious metal consistently hits new all time highs. The current correlation to the S&P 500 has only happened two times in history; right now and October of 2007. 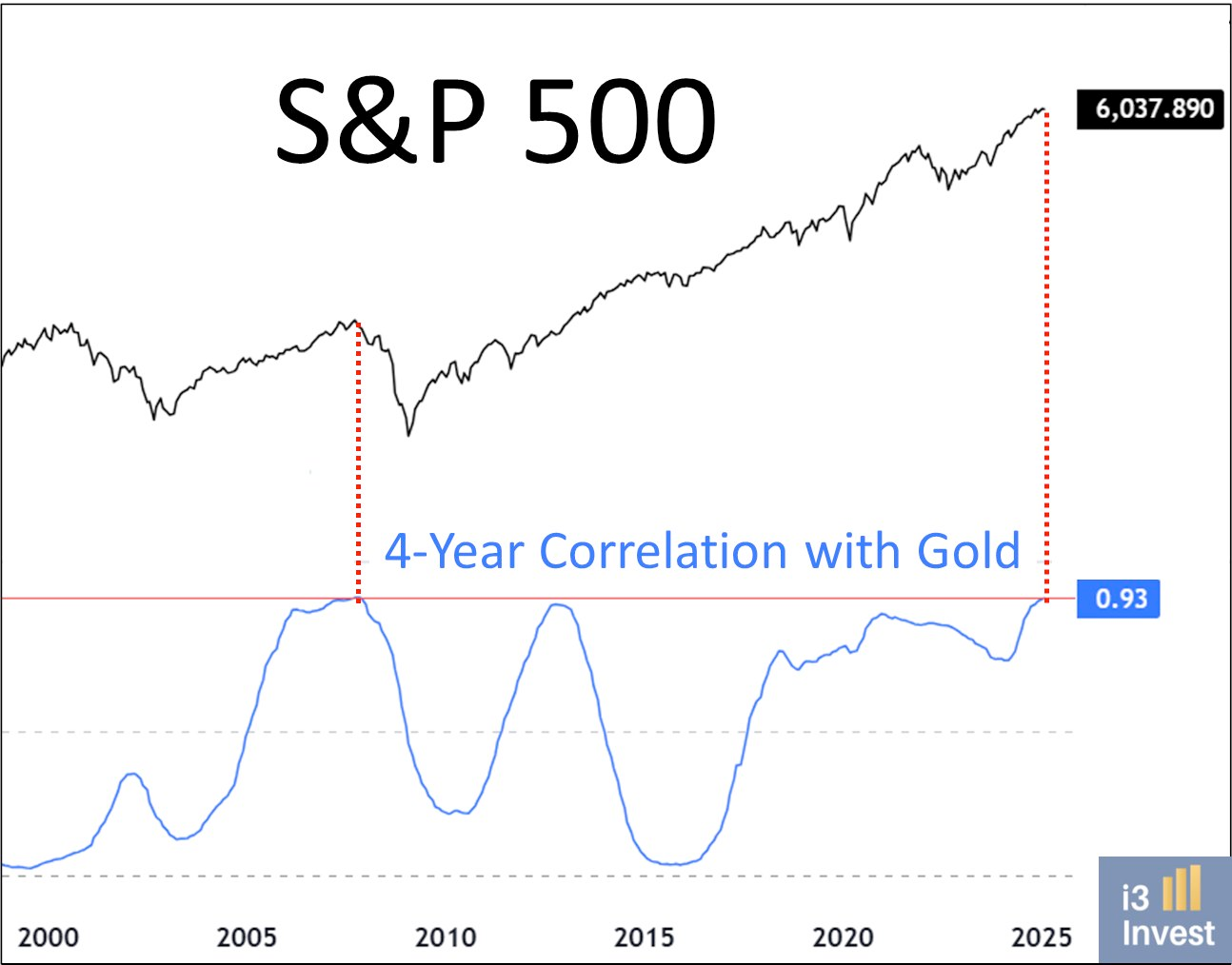 Institutional investors and nation states are piling into gold at an unprecedented pace. This signals that they are preparing for something to break. The catalysts for the exodus of gold from London to the US and from paper gold to physical gold are fears over Trump's tariffs, institutions and governments preparing for a potential monetary reset, and fears of a looming liquidity crisis as liquidity in the reverse repo market dries up. Uncertainty and chaos rule the day and we are witnessing a flight to safety. Many of you are probably asking, "Why isn't bitcoin moving?!" That's a good question. Considering everything mentioned above one would think that bitcoin would be on the move toward new all time highs as well. Having been following bitcoin for twelve years your Uncle Marty has developed some pattern recognition when it comes to this market. Upward bitcoin price movements typically happen in a staircase fashion. Meaning that it trends up and to the right over the long-run with quick bursts to higher levels followed by small corrections and consolidation periods. If I had to guess, we are currently in a consolidation period that should come to an end at some point in the next few months. In recent years, gold has moved higher first and bitcoin has followed. Typically outperforming gold significantly. I find it hard to believe that this relationship is going to end any time soon. Especially considering the geopolitical and economic backdrop. ## Luke Gromen Warns Bitcoin Holders: Historical Currency Revaluations Show Speed Matters During my recent conversation with Luke Gromen, he raised a sobering point about the velocity of monetary regime changes. Drawing from historical examples, including a Ukrainian family who saw their savings devalue from "five cars to one month's groceries" over a single weekend, Luke emphasized that Americans are uniquely blind to how quickly these transitions can occur. The current stress in our financial system - from Treasury market dynamics to global trade tensions - suggests we're approaching a similar inflection point. *"What if they do it on Friday night like they did with Trump coin and you wake up and gold's up 1,000% by the time you're up on Saturday morning, what are you going to do? You're going to sell your bonds and buy gold on Saturday?"* - Luke Gromen 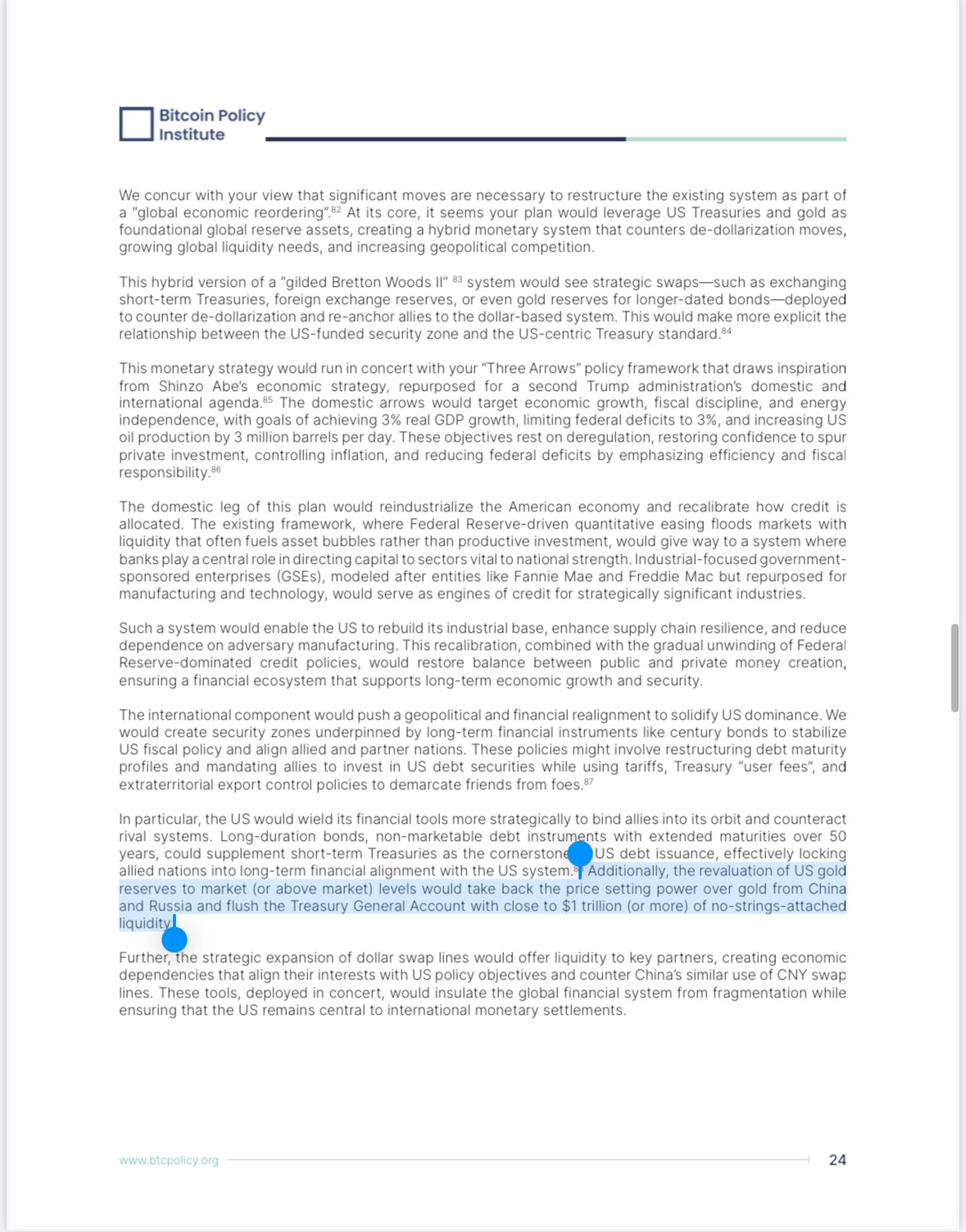 This warning shouldn't be taken lightly. Those waiting for clear signals before acquiring bitcoin may find themselves locked out of the transition entirely. Luke's analysis suggests that rather than a gradual shift, we're more likely to see a compressed timeframe where major monetary changes happen over days or weeks, not months or years. The recent Trump coin phenomenon, while different in nature, demonstrates how quickly markets can move when sentiment shifts dramatically. TLDR: Major monetary changes happen fast - don't wait to stack sats. Check out the full podcast [here](https://www.youtube.com/watch?v=RCeWQHATWYU&t=61s&ab_channel=TFTC&ref=tftc.io) for more on DeepSeek's impact on AI markets, Colombia's trade negotiations, and Scott Percent's three arrows for economic reform. ## Headlines of the Day U.S. Faces $1.67B Annual Cost Spike on Single Bond Rollover - via [X](https://x.com/TFTC21/status/1889454272842268982) BlackRock: Bitcoin is Monetary Hedge, Ethereum is Tech Play - via [X](https://x.com/BitcoinNewsCom/status/1889396849880268814) Lummis: SBR Could Slash U.S. Debt by 50% in Two Decades - via [X](https://x.com/cryptonwsuk/status/1888565117047951869) Fold Launches Bitcoin Rewards Visa Credit Card - via [Business Wire](https://www.businesswire.com/news/home/20250211765772/en/Fold-Launches-Revolutionary-Bitcoin-Rewards-Visa-Credit-Card) Obscura VPN launches with a MacOS product - via [nobsbitcoin.com](https://www.nobsbitcoin.com/obscura-vpn-is-now-available-on-macos/) ## Bitcoin Lesson of the Day The SegWit (Segregated Witness) upgrade in August 2017 made two key changes to Bitcoin. First, it moved transaction signatures to a separate part of the data, fixing "transaction malleability" by preventing nodes from modifying transaction IDs. Second, it increased effective block capacity by introducing "weight units" that gave signature data a 75% discount, allowing blocks to grow from 1MB to about 1.8MB. As a "soft fork," SegWit remained compatible with older Bitcoin software. The upgrade activated at block 481,824 after 95% of miners signaled support. This approach allowed Bitcoin to increase capacity and fix technical issues while maintaining network compatibility. [SegWit - Learnmeabitcoin.com](https://learnmeabitcoin.com/beginners/guide/segwit/?ref=tftc.io) ICYMI Fold opened the waiting list for the new Bitcoin Rewards Credit Card. Fold cardholders will get unlimited 2% cash back in sats. [Get on the waiting list now](https://foldapp.com/credit-card?r=BgwRS) before it fills up! $200k worth of prizes are up for grabs . The Fold Bitcoin Rewards Credit Card waitlist is live! *Ten31, the largest bitcoin-focused investor, has deployed $150M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/funds.* Subscribe to our YouTube channels and follow us on Nostr and X: [TFTC YouTube](https://www.youtube.com/tftc21) [Bitcoin Brief YouTube](https://www.youtube.com/@BTCBrief) [TFTC on Nostr](https://primal.net/tftc) [TFTC on X](https://x.com/tftc21)
@ 85bdb587:7339d672
2025-02-12 15:24:11## Chart of the Day While this is a bitcoin focused rag, I think it is important for any of you who read this to begin paying attention to gold markets if you haven't already. There has been an ongoing exodus of physical gold from London vaults and a rapid acceleration of gold being moved to the three biggest vaults in the United States in recent weeks. More gold has flooded into the US vaults over the first two months of this year than at the peak of the flight to safety during the beginning of the COVID lock downs. 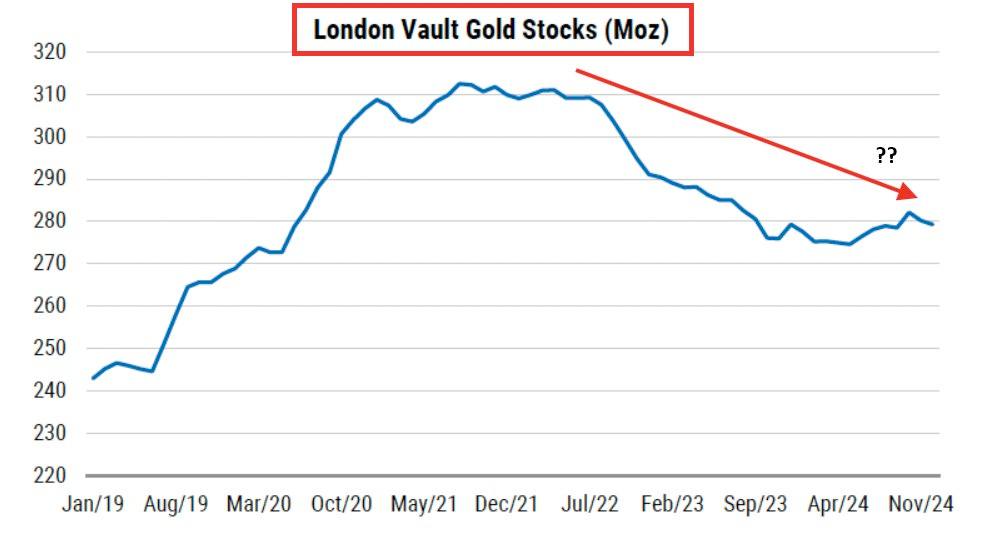 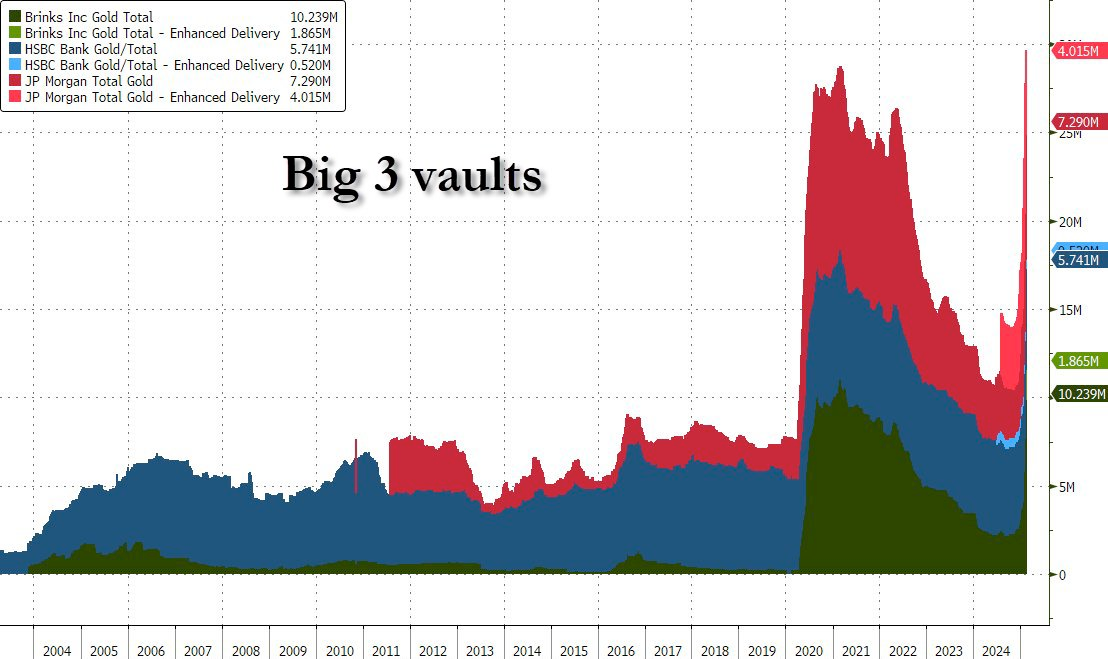 This is particularly perplexing considering the fact that equities are flat or up on the year, depending on the index you like to follow. Gold outperformed the S&P 500 significantly in 2024 and its momentum hasn't slowed down a bit in 2025 as the precious metal consistently hits new all time highs. The current correlation to the S&P 500 has only happened two times in history; right now and October of 2007. 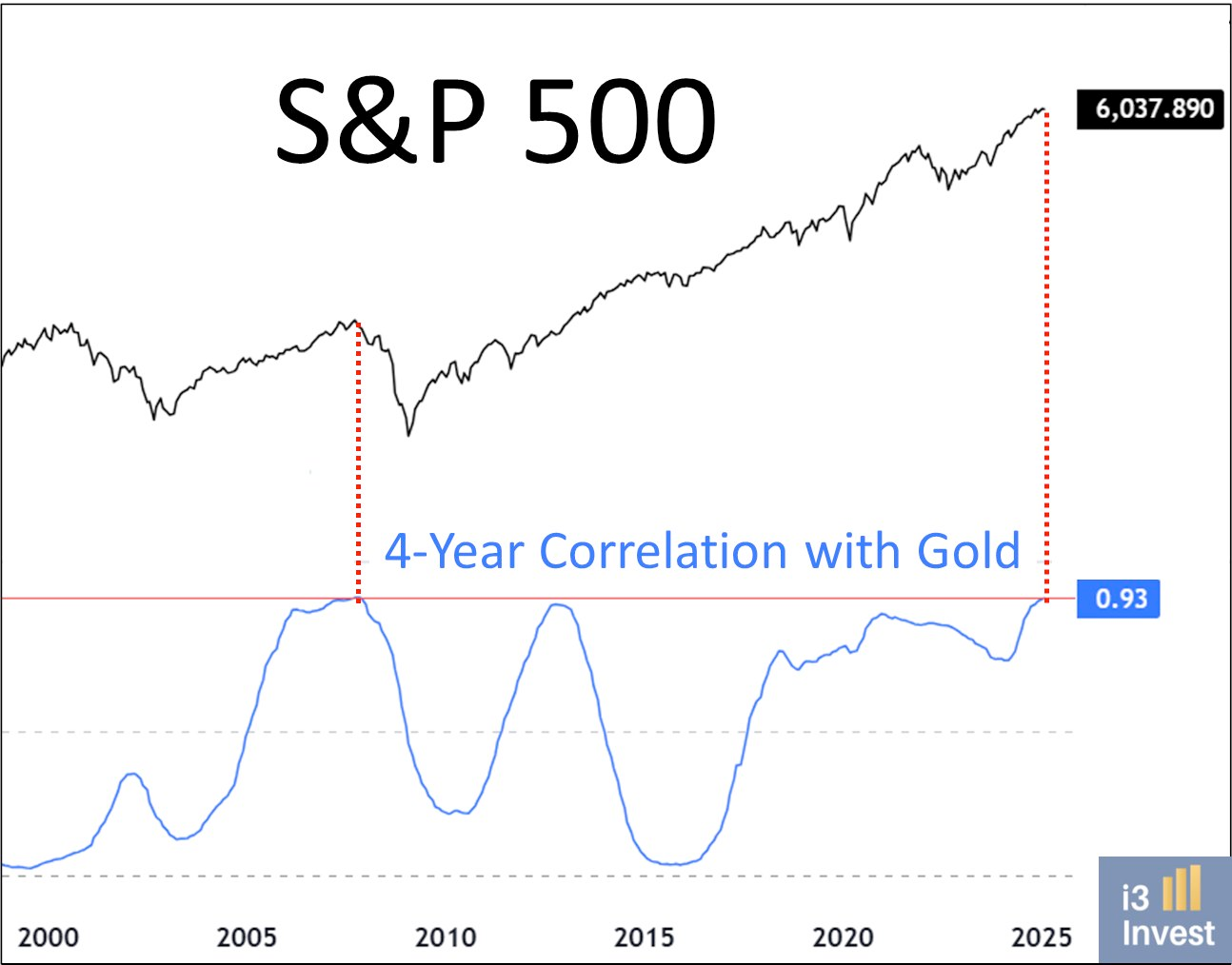 Institutional investors and nation states are piling into gold at an unprecedented pace. This signals that they are preparing for something to break. The catalysts for the exodus of gold from London to the US and from paper gold to physical gold are fears over Trump's tariffs, institutions and governments preparing for a potential monetary reset, and fears of a looming liquidity crisis as liquidity in the reverse repo market dries up. Uncertainty and chaos rule the day and we are witnessing a flight to safety. Many of you are probably asking, "Why isn't bitcoin moving?!" That's a good question. Considering everything mentioned above one would think that bitcoin would be on the move toward new all time highs as well. Having been following bitcoin for twelve years your Uncle Marty has developed some pattern recognition when it comes to this market. Upward bitcoin price movements typically happen in a staircase fashion. Meaning that it trends up and to the right over the long-run with quick bursts to higher levels followed by small corrections and consolidation periods. If I had to guess, we are currently in a consolidation period that should come to an end at some point in the next few months. In recent years, gold has moved higher first and bitcoin has followed. Typically outperforming gold significantly. I find it hard to believe that this relationship is going to end any time soon. Especially considering the geopolitical and economic backdrop. ## Luke Gromen Warns Bitcoin Holders: Historical Currency Revaluations Show Speed Matters During my recent conversation with Luke Gromen, he raised a sobering point about the velocity of monetary regime changes. Drawing from historical examples, including a Ukrainian family who saw their savings devalue from "five cars to one month's groceries" over a single weekend, Luke emphasized that Americans are uniquely blind to how quickly these transitions can occur. The current stress in our financial system - from Treasury market dynamics to global trade tensions - suggests we're approaching a similar inflection point. *"What if they do it on Friday night like they did with Trump coin and you wake up and gold's up 1,000% by the time you're up on Saturday morning, what are you going to do? You're going to sell your bonds and buy gold on Saturday?"* - Luke Gromen 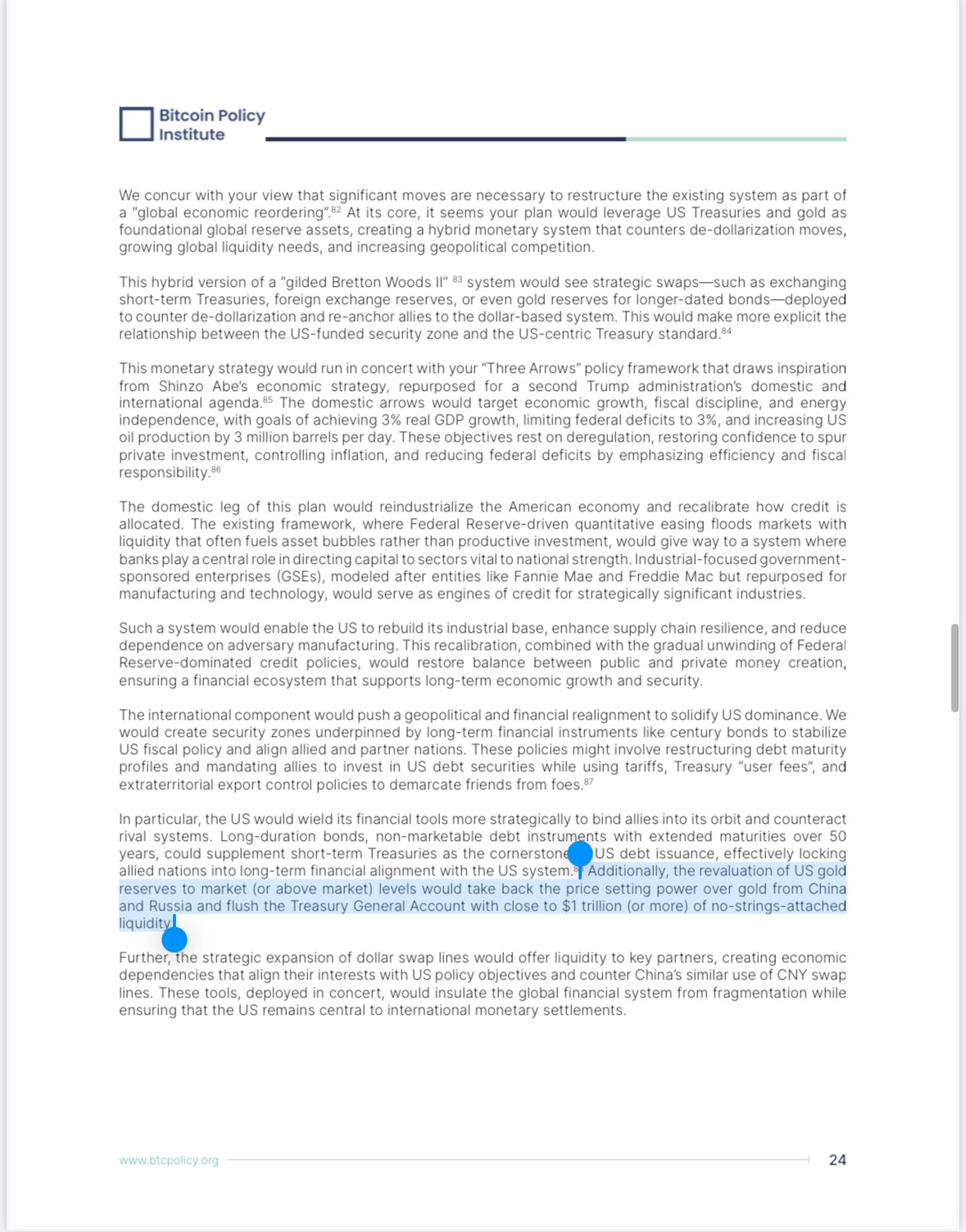 This warning shouldn't be taken lightly. Those waiting for clear signals before acquiring bitcoin may find themselves locked out of the transition entirely. Luke's analysis suggests that rather than a gradual shift, we're more likely to see a compressed timeframe where major monetary changes happen over days or weeks, not months or years. The recent Trump coin phenomenon, while different in nature, demonstrates how quickly markets can move when sentiment shifts dramatically. TLDR: Major monetary changes happen fast - don't wait to stack sats. Check out the full podcast [here](https://www.youtube.com/watch?v=RCeWQHATWYU&t=61s&ab_channel=TFTC&ref=tftc.io) for more on DeepSeek's impact on AI markets, Colombia's trade negotiations, and Scott Percent's three arrows for economic reform. ## Headlines of the Day U.S. Faces $1.67B Annual Cost Spike on Single Bond Rollover - via [X](https://x.com/TFTC21/status/1889454272842268982) BlackRock: Bitcoin is Monetary Hedge, Ethereum is Tech Play - via [X](https://x.com/BitcoinNewsCom/status/1889396849880268814) Lummis: SBR Could Slash U.S. Debt by 50% in Two Decades - via [X](https://x.com/cryptonwsuk/status/1888565117047951869) Fold Launches Bitcoin Rewards Visa Credit Card - via [Business Wire](https://www.businesswire.com/news/home/20250211765772/en/Fold-Launches-Revolutionary-Bitcoin-Rewards-Visa-Credit-Card) Obscura VPN launches with a MacOS product - via [nobsbitcoin.com](https://www.nobsbitcoin.com/obscura-vpn-is-now-available-on-macos/) ## Bitcoin Lesson of the Day The SegWit (Segregated Witness) upgrade in August 2017 made two key changes to Bitcoin. First, it moved transaction signatures to a separate part of the data, fixing "transaction malleability" by preventing nodes from modifying transaction IDs. Second, it increased effective block capacity by introducing "weight units" that gave signature data a 75% discount, allowing blocks to grow from 1MB to about 1.8MB. As a "soft fork," SegWit remained compatible with older Bitcoin software. The upgrade activated at block 481,824 after 95% of miners signaled support. This approach allowed Bitcoin to increase capacity and fix technical issues while maintaining network compatibility. [SegWit - Learnmeabitcoin.com](https://learnmeabitcoin.com/beginners/guide/segwit/?ref=tftc.io) ICYMI Fold opened the waiting list for the new Bitcoin Rewards Credit Card. Fold cardholders will get unlimited 2% cash back in sats. [Get on the waiting list now](https://foldapp.com/credit-card?r=BgwRS) before it fills up! $200k worth of prizes are up for grabs . The Fold Bitcoin Rewards Credit Card waitlist is live! *Ten31, the largest bitcoin-focused investor, has deployed $150M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/funds.* Subscribe to our YouTube channels and follow us on Nostr and X: [TFTC YouTube](https://www.youtube.com/tftc21) [Bitcoin Brief YouTube](https://www.youtube.com/@BTCBrief) [TFTC on Nostr](https://primal.net/tftc) [TFTC on X](https://x.com/tftc21) @ 94a6a78a:0ddf320e
2025-02-12 15:05:48Azzamo is more than just a relay provider—it’s a **high-performance network** designed to make Nostr **faster, smoother, and more reliable** for everyone. Whether you're **posting notes, zapping sats, sharing media, or sending DMs**, Azzamo keeps your Nostr experience **seamless and efficient**. Nostr is unstoppable, but **not all relays are the same**. Some are **slow, unreliable, or disappear overnight**, while others get **overloaded**, making message delivery **inconsistent**. Azzamo is built differently—offering **fast, stable, and globally distributed relays** to ensure **low-latency, high-speed connections**, no matter where you are. --- ## **🌍 Premium Relays for Maximum Performance** Azzamo **Premium Relays** are optimized for **speed, reliability, and uptime**, available exclusively to **Premium users**: 📡 **Azzamo Premium Relays:** - **Europe:** `wss://relay.azzamo.net` - **America:** `wss://us.azzamo.net` - **Asia:** `wss://asia.azzamo.net` Add **Azzamo Premium Time** to **unlock unlimited, high-speed access** across these global relays. 🔗 **Get Premium:** [azzamo.net/premium](https://azzamo.net/premium) --- ## **🆓 Freemium Relays – Free for Everyone** Azzamo believes in **keeping Nostr open** and accessible to all. That’s why we offer **free relays for everyone**, with **no rate limits for Premium members** 📡 **Freemium Relays:** - **Free Relay:** `wss://nostr.azzamo.net` – Open to all. - **Inbox Relay:** `wss://inbox.azzamo.net` – Reliable for DMs & group messages. By offering both **free and premium options**, Azzamo ensures that **anyone can use Nostr, while also funding the infrastructure that keeps it running smoothly.** --- ## **🛡️ Minimal Moderation, Maximum Transparency** Nostr is about **free speech**, but that doesn’t mean **zero moderation.** Azzamo follows a **minimal moderation policy** to keep relays **functional and spam-free** while maintaining **transparency** in enforcement.\ \ 🚫 **Spam & network abuse**\ 🚫 **Illegal content (CSAM, fraud, malware, scams)**\ 🚫 **Impersonation & identity abuse** We also maintain a **public Ban API** for **transparent moderation decisions**. 📖 **More on our Ban API:** [azzamo.net/introducing-the-azzamo-ban-api](https://azzamo.net/introducing-the-azzamo-ban-api) --- ## **🚀 Get Started with Azzamo Relays Today!** 🔗 **Connect now:**\ 📡 `wss://nostr.azzamo.net` (Freemium Free Relay)\ 📬 `wss://inbox.azzamo.net` (Freemium Inbox Relay)\ 📡 `wss://relay.azzamo.net` (Premium Europe Relay)\ 📡 `wss://us.azzamo.net` (Premium Americas Relay)\ 📡 `wss://asia.azzamo.net` (Premium Asia Relay) Nostr is growing fast. **Make sure your relays can keep up.** 🚀 #azzamo #grownostr #nostr #relay #relays #premiumrelay #paidrelay
@ 94a6a78a:0ddf320e
2025-02-12 15:05:48Azzamo is more than just a relay provider—it’s a **high-performance network** designed to make Nostr **faster, smoother, and more reliable** for everyone. Whether you're **posting notes, zapping sats, sharing media, or sending DMs**, Azzamo keeps your Nostr experience **seamless and efficient**. Nostr is unstoppable, but **not all relays are the same**. Some are **slow, unreliable, or disappear overnight**, while others get **overloaded**, making message delivery **inconsistent**. Azzamo is built differently—offering **fast, stable, and globally distributed relays** to ensure **low-latency, high-speed connections**, no matter where you are. --- ## **🌍 Premium Relays for Maximum Performance** Azzamo **Premium Relays** are optimized for **speed, reliability, and uptime**, available exclusively to **Premium users**: 📡 **Azzamo Premium Relays:** - **Europe:** `wss://relay.azzamo.net` - **America:** `wss://us.azzamo.net` - **Asia:** `wss://asia.azzamo.net` Add **Azzamo Premium Time** to **unlock unlimited, high-speed access** across these global relays. 🔗 **Get Premium:** [azzamo.net/premium](https://azzamo.net/premium) --- ## **🆓 Freemium Relays – Free for Everyone** Azzamo believes in **keeping Nostr open** and accessible to all. That’s why we offer **free relays for everyone**, with **no rate limits for Premium members** 📡 **Freemium Relays:** - **Free Relay:** `wss://nostr.azzamo.net` – Open to all. - **Inbox Relay:** `wss://inbox.azzamo.net` – Reliable for DMs & group messages. By offering both **free and premium options**, Azzamo ensures that **anyone can use Nostr, while also funding the infrastructure that keeps it running smoothly.** --- ## **🛡️ Minimal Moderation, Maximum Transparency** Nostr is about **free speech**, but that doesn’t mean **zero moderation.** Azzamo follows a **minimal moderation policy** to keep relays **functional and spam-free** while maintaining **transparency** in enforcement.\ \ 🚫 **Spam & network abuse**\ 🚫 **Illegal content (CSAM, fraud, malware, scams)**\ 🚫 **Impersonation & identity abuse** We also maintain a **public Ban API** for **transparent moderation decisions**. 📖 **More on our Ban API:** [azzamo.net/introducing-the-azzamo-ban-api](https://azzamo.net/introducing-the-azzamo-ban-api) --- ## **🚀 Get Started with Azzamo Relays Today!** 🔗 **Connect now:**\ 📡 `wss://nostr.azzamo.net` (Freemium Free Relay)\ 📬 `wss://inbox.azzamo.net` (Freemium Inbox Relay)\ 📡 `wss://relay.azzamo.net` (Premium Europe Relay)\ 📡 `wss://us.azzamo.net` (Premium Americas Relay)\ 📡 `wss://asia.azzamo.net` (Premium Asia Relay) Nostr is growing fast. **Make sure your relays can keep up.** 🚀 #azzamo #grownostr #nostr #relay #relays #premiumrelay #paidrelay @ dd664d5e:5633d319
2025-01-07 19:57:14## Hodling Bitcoin does not make you a capitalist I've noticed that Bitcoin-mindedness seems to lead some people to communistic thinking because it's a hard-limited form of capital. Marx, like most Bitcoiners, heavily discounted the possibility of economic growth or transformation changing the economy enough to undermine some minority's control of some form of capital. What few today understand, is that many of the Dirty Capitalists of Marx's era actually agreed with him; they were just disdainful of labor and worried that the workers finding out that Marxism is correct about the nature of capitalism would cause unrest. They were the original HFSP crowd. This was the basic idea, that Marx had, and that many Bitcoiners would agree with: > Capital is strictly limited and the people that control it can keep labor from attaining any, except when their labor is necessary. And, as we know, automation will make human labor increasingly unnecessary. ## The math doesn't check out  That underlies all of the calculations of "Well, if I just grab this Bitcoin wallet and hodl for twenty years, then it will grow in value to equal half of everything in existence and then I can just buy up half the planet and rule over everyone like a god." This is economic nonsense because it assumes that: 1) the value of all things remains static over time, 2) purchasing something with money gives you ownership of it, 3) people will always use that specific money (or any money, at all!) for all transactions, 4) there is no such thing as opportunity cost, 5) people will always value money more than any other thing, and therefore be willing to always trade it for anything else, 6) humans are passive, defenseless, and easy to rule over, 7) someone who is preoccupied with hodling an asset steadily and sharply rising in price would ever be emotionally ready to part with it. ## All monies can die. People use money for everything because it is easy, fast and cheap. If money becomes too precious or scarce, they will simply switch to using other things (as we saw with gold). Humans replace tools that aren't working well, with those that work better, and money is just another tool. Bitcoin is more divisible than gold, but that won't matter, if enough of it is held by too few. This is why there's a natural cap on the price of a money and why human productivity _in the here and now_ is not irrelevant or in vain.
@ dd664d5e:5633d319
2025-01-07 19:57:14## Hodling Bitcoin does not make you a capitalist I've noticed that Bitcoin-mindedness seems to lead some people to communistic thinking because it's a hard-limited form of capital. Marx, like most Bitcoiners, heavily discounted the possibility of economic growth or transformation changing the economy enough to undermine some minority's control of some form of capital. What few today understand, is that many of the Dirty Capitalists of Marx's era actually agreed with him; they were just disdainful of labor and worried that the workers finding out that Marxism is correct about the nature of capitalism would cause unrest. They were the original HFSP crowd. This was the basic idea, that Marx had, and that many Bitcoiners would agree with: > Capital is strictly limited and the people that control it can keep labor from attaining any, except when their labor is necessary. And, as we know, automation will make human labor increasingly unnecessary. ## The math doesn't check out  That underlies all of the calculations of "Well, if I just grab this Bitcoin wallet and hodl for twenty years, then it will grow in value to equal half of everything in existence and then I can just buy up half the planet and rule over everyone like a god." This is economic nonsense because it assumes that: 1) the value of all things remains static over time, 2) purchasing something with money gives you ownership of it, 3) people will always use that specific money (or any money, at all!) for all transactions, 4) there is no such thing as opportunity cost, 5) people will always value money more than any other thing, and therefore be willing to always trade it for anything else, 6) humans are passive, defenseless, and easy to rule over, 7) someone who is preoccupied with hodling an asset steadily and sharply rising in price would ever be emotionally ready to part with it. ## All monies can die. People use money for everything because it is easy, fast and cheap. If money becomes too precious or scarce, they will simply switch to using other things (as we saw with gold). Humans replace tools that aren't working well, with those that work better, and money is just another tool. Bitcoin is more divisible than gold, but that won't matter, if enough of it is held by too few. This is why there's a natural cap on the price of a money and why human productivity _in the here and now_ is not irrelevant or in vain. @ 5d4b6c8d:8a1c1ee3
2025-02-12 14:36:40Here are today's picks using my proprietary betting strategy at [Freebitcoin](https://freebitco.in/?r=51325722). For details about what Risk Balanced Odds Arbitrage is and why it works see https://stacker.news/items/342765/r/Undisciplined. For a hypothetical 1k-ish wager on each match, distribute your sats as follows: | Outcome 1 | Outcome 2 | Outcome 3 | Bet 1 | Bet 2 | Bet 3 | |--------------|-------------|--------------|-------|-------|-------| | Juventus| Inter Milan| Draw | 294| 435| 303| | Tottenham| Man United| Draw | 406| 357| 266| | Liverpool| Wolves| Draw | 833| 67| 125| | Valladolid| Sevilla| Draw | 222| 500| 289| | Real Betis| Real Sociedad| Draw | 393| 321| 313| | Osasuna| Real Madrid| Draw | 174| 619| 227| | Barcelona| Rayo Vallecano| Draw | 818| 80| 133| | Atletico Madrid| Celta Vigo| Draw | 692| 118| 217| I'll be curious to see how @Coinsreporter does with his modified RBOA. On the most recently completed sets of RBOA, I lost 700 sats on about 50k wagered. I'm not sure if that's just normal variance or if it's due to matches not being posted as far in advance, which reduces the early mover bonus. I still haven't precisely identified where the threshold is, but it might be worth skipping any of these with a "time weight multiplier" lower than 90. ---------- A note of caution about Freebitcoin: they recorded the wrong outcome for last week's Bills vs Ravens game and as of yet have not corrected it. I recall one other instance of something similar happening, so proceed with caution. This RBOA strategy is largely immune from that problem, but be aware of it when just betting on one outcome. originally posted at https://stacker.news/items/883708
@ 5d4b6c8d:8a1c1ee3
2025-02-12 14:36:40Here are today's picks using my proprietary betting strategy at [Freebitcoin](https://freebitco.in/?r=51325722). For details about what Risk Balanced Odds Arbitrage is and why it works see https://stacker.news/items/342765/r/Undisciplined. For a hypothetical 1k-ish wager on each match, distribute your sats as follows: | Outcome 1 | Outcome 2 | Outcome 3 | Bet 1 | Bet 2 | Bet 3 | |--------------|-------------|--------------|-------|-------|-------| | Juventus| Inter Milan| Draw | 294| 435| 303| | Tottenham| Man United| Draw | 406| 357| 266| | Liverpool| Wolves| Draw | 833| 67| 125| | Valladolid| Sevilla| Draw | 222| 500| 289| | Real Betis| Real Sociedad| Draw | 393| 321| 313| | Osasuna| Real Madrid| Draw | 174| 619| 227| | Barcelona| Rayo Vallecano| Draw | 818| 80| 133| | Atletico Madrid| Celta Vigo| Draw | 692| 118| 217| I'll be curious to see how @Coinsreporter does with his modified RBOA. On the most recently completed sets of RBOA, I lost 700 sats on about 50k wagered. I'm not sure if that's just normal variance or if it's due to matches not being posted as far in advance, which reduces the early mover bonus. I still haven't precisely identified where the threshold is, but it might be worth skipping any of these with a "time weight multiplier" lower than 90. ---------- A note of caution about Freebitcoin: they recorded the wrong outcome for last week's Bills vs Ravens game and as of yet have not corrected it. I recall one other instance of something similar happening, so proceed with caution. This RBOA strategy is largely immune from that problem, but be aware of it when just betting on one outcome. originally posted at https://stacker.news/items/883708 @ 207ad2a0:e7cca7b0
2025-01-07 03:46:04*Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my [free to read/share attempt to write a novel](https://untitlednovel.dns7.top/contents/), but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.* Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end. Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:  and after a number of outputs, selected this one to work on:  The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.  The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.  At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.  At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:  Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story. #### The AI Generated Elephant in the Room If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it. I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points. I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs.
@ 207ad2a0:e7cca7b0
2025-01-07 03:46:04*Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my [free to read/share attempt to write a novel](https://untitlednovel.dns7.top/contents/), but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.* Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end. Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:  and after a number of outputs, selected this one to work on:  The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.  The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.  At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.  At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:  Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story. #### The AI Generated Elephant in the Room If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it. I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points. I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs. @ dd664d5e:5633d319
2025-01-06 20:36:17_Ingredients_ * 1 kg of pork roast with rind, such as shoulder or a lean belly * 1 bottle of beer, light or dark * chopped German-style mirepoix (best combination, for this recipe, includes celery root, carrot, red onion, and leeks) * salt, pepper, nutmeg * 1 diced garlic clove _Directions_ 1. Spread the vegetables on the bottom of the roasting pan. 2. Pour half the beer over the roast. (Drink the other half.) 3. Season the meat, to taste. 4. Roast the meat at 180 °C, until done (depends upon the weight of the roast). 5. Remove the meat from the oven, and wrap in aluminum foil. 6. Pour 2-3 cups of water into the roasting pan. 7. Pour/scrape everything from the pan into a sieve over a sauce pot. 8. Press the vegetables against the sieve, with the back of a spoon, to ensure that you get all that good dripping flavor into the sauce. 9. Defat the sauce with a grease separator, then pour it back into the pot. 10. Thicken the sauce, slightly (it should remain slightly watery, and not turn into a gravy), according to your usual method. 11. Open the foil and slice the roast. 12. Serve with the sauce.        
@ dd664d5e:5633d319
2025-01-06 20:36:17_Ingredients_ * 1 kg of pork roast with rind, such as shoulder or a lean belly * 1 bottle of beer, light or dark * chopped German-style mirepoix (best combination, for this recipe, includes celery root, carrot, red onion, and leeks) * salt, pepper, nutmeg * 1 diced garlic clove _Directions_ 1. Spread the vegetables on the bottom of the roasting pan. 2. Pour half the beer over the roast. (Drink the other half.) 3. Season the meat, to taste. 4. Roast the meat at 180 °C, until done (depends upon the weight of the roast). 5. Remove the meat from the oven, and wrap in aluminum foil. 6. Pour 2-3 cups of water into the roasting pan. 7. Pour/scrape everything from the pan into a sieve over a sauce pot. 8. Press the vegetables against the sieve, with the back of a spoon, to ensure that you get all that good dripping flavor into the sauce. 9. Defat the sauce with a grease separator, then pour it back into the pot. 10. Thicken the sauce, slightly (it should remain slightly watery, and not turn into a gravy), according to your usual method. 11. Open the foil and slice the roast. 12. Serve with the sauce.         @ e6817453:b0ac3c39
2025-01-05 14:29:17## The Rise of Graph RAGs and the Quest for Data Quality As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence. ## Booming Interest in Graph RAGs Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can: * **Enhance LLM Outputs:** By grounding responses in structured knowledge, graphs significantly reduce hallucinations. * **Support Complex Queries:** Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving. Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs? ## Data Quality: The Foundation of Effective Graphs A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why: * **Richness of Entities:** Effective retrieval depends on graphs populated with rich, detailed entities. * **Freedom from Hallucinations:** Poorly constructed graphs amplify inaccuracies rather than mitigating them. Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs. ## Hybrid Graph RAGs and Variations While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that: * Handle diverse data sources with ease. * Offer improved adaptability to complex queries. Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing. ## Ontology: The Key to Graph Construction Quality Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for: * **Defining Relationships:** Clarifying how concepts connect within a domain. * **Validating Graph Structures:** Ensuring constructed graphs are logically sound and align with domain-specific realities. Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs? ## How to Build Ontology Expertise in a Startup Team For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach: 1. **Assign a Knowledge Champion:** Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering. 2. **Provide Training:** Invest in courses, workshops, or certifications in knowledge graph and ontology creation. 3. **Leverage Partnerships:** Collaborate with academic institutions, domain experts, or consultants to build initial frameworks. 4. **Utilize Tools:** Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process. 5. **Iterate with Feedback:** Continuously refine ontologies through collaboration with domain experts and iterative testing. So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts. You could read about barefoot experts in my article : Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise. ## How to Find or Create Ontologies For teams venturing into Graph RAGs, several strategies can help address the ontology gap: 1. **Leverage Existing Ontologies:** Many industries and domains already have open ontologies. For instance: * **Public Knowledge Graphs:** Resources like Wikipedia’s graph offer a wealth of structured knowledge. * **Industry Standards:** Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields. * **Business Framework Ontology (BFO):** A valuable resource for enterprises looking to define business processes and structures. 1. **Build In-House Expertise:** If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation. 2. **Utilize LLMs for Ontology Construction:** Interestingly, LLMs themselves can act as a starting point for ontology development: * **Prompt-Based Extraction:** LLMs can generate draft ontologies by leveraging their extensive training on graph data. * **Domain Expert Refinement:** Combine LLM-generated structures with insights from domain experts to create tailored ontologies. ## Parallel Ontology and Graph Extraction An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as: * **Detecting Hallucinations:** Differentiating between genuine insights and AI-generated inaccuracies. * **Ensuring Completeness:** Ensuring no critical concepts are overlooked during extraction. Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method. ## LLMs as Ontologists While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to: * **Generate Skeleton Ontologies:** Prompt LLMs with domain-specific information to draft initial ontology structures. * **Validate and Refine Ontologies:** Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance. However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes. ## Final Thoughts: Unlocking the Power of Graph RAGs The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools. As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding. Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation!
@ e6817453:b0ac3c39
2025-01-05 14:29:17## The Rise of Graph RAGs and the Quest for Data Quality As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence. ## Booming Interest in Graph RAGs Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can: * **Enhance LLM Outputs:** By grounding responses in structured knowledge, graphs significantly reduce hallucinations. * **Support Complex Queries:** Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving. Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs? ## Data Quality: The Foundation of Effective Graphs A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why: * **Richness of Entities:** Effective retrieval depends on graphs populated with rich, detailed entities. * **Freedom from Hallucinations:** Poorly constructed graphs amplify inaccuracies rather than mitigating them. Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs. ## Hybrid Graph RAGs and Variations While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that: * Handle diverse data sources with ease. * Offer improved adaptability to complex queries. Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing. ## Ontology: The Key to Graph Construction Quality Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for: * **Defining Relationships:** Clarifying how concepts connect within a domain. * **Validating Graph Structures:** Ensuring constructed graphs are logically sound and align with domain-specific realities. Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs? ## How to Build Ontology Expertise in a Startup Team For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach: 1. **Assign a Knowledge Champion:** Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering. 2. **Provide Training:** Invest in courses, workshops, or certifications in knowledge graph and ontology creation. 3. **Leverage Partnerships:** Collaborate with academic institutions, domain experts, or consultants to build initial frameworks. 4. **Utilize Tools:** Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process. 5. **Iterate with Feedback:** Continuously refine ontologies through collaboration with domain experts and iterative testing. So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts. You could read about barefoot experts in my article : Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise. ## How to Find or Create Ontologies For teams venturing into Graph RAGs, several strategies can help address the ontology gap: 1. **Leverage Existing Ontologies:** Many industries and domains already have open ontologies. For instance: * **Public Knowledge Graphs:** Resources like Wikipedia’s graph offer a wealth of structured knowledge. * **Industry Standards:** Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields. * **Business Framework Ontology (BFO):** A valuable resource for enterprises looking to define business processes and structures. 1. **Build In-House Expertise:** If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation. 2. **Utilize LLMs for Ontology Construction:** Interestingly, LLMs themselves can act as a starting point for ontology development: * **Prompt-Based Extraction:** LLMs can generate draft ontologies by leveraging their extensive training on graph data. * **Domain Expert Refinement:** Combine LLM-generated structures with insights from domain experts to create tailored ontologies. ## Parallel Ontology and Graph Extraction An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as: * **Detecting Hallucinations:** Differentiating between genuine insights and AI-generated inaccuracies. * **Ensuring Completeness:** Ensuring no critical concepts are overlooked during extraction. Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method. ## LLMs as Ontologists While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to: * **Generate Skeleton Ontologies:** Prompt LLMs with domain-specific information to draft initial ontology structures. * **Validate and Refine Ontologies:** Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance. However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes. ## Final Thoughts: Unlocking the Power of Graph RAGs The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools. As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding. Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation! @ c4b5369a:b812dbd6
2025-02-12 12:23:40 ### Unidirectional payment channels revisited #### Nodeless lightning - Reduce ecash mints custodial risk --- ### Sats N Facts The nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx unconference has just wrapped up. And what a blast it was. In the heart of northern Thailand, developers, researchers, content creators and more, came together to share ideas on how Bitcoin, Nostr and other free protocols are being used everyday to liberate people. Not only were stories shared from different community leaders on how embracing bitcoin has empowered them and their communities, but a big goal of the unconference was to bring bitcoin engineers and developers from various domains together in one room, unstructured, chaotic, and let them do their thing. At first, I thought not having a schedule might be boring, but oh boy was I wrong. There was so much stuff going on, it was hard to choose which session I would have to miss! ### Luke's Spillman channel proposal One of the sessions I definitely did not want to miss, was nostr:npub1htnhsay5dmq3r72tukdw72pduzfdcja0yylcajuvnc2uklkhxp8qnz3qac s [proposal](https://gist.github.com/lukechilds/307341239beac72c9d8cfe3198f9bfff) > Ecash mints funded with Spillman channels: The ultimate nodeless Lightning wallet . In true unconference fashion, he announced in the main room that the session was about to start, and that the people that are interested should meet him in the whiteboard corner in 10 minutes. The corner was packed, and Luke explained his proposal. ### What's a "[Spillman channel](https://en.bitcoin.it/wiki/Payment_channels#Spillman-style_payment_channels)"? Essentially when we are talking about Spillman channels, what is meant are unidirectional payment channels (or [CLTV-style channels](https://en.bitcoin.it/wiki/Payment_channels#CLTV-style_payment_channels)). An unidirectional payment channel means, only one party can send payments, but not receive, and the other party can only receive, but not send. They also expire after a predetermined amount of time, and must be closed.  At first glance, this might look kinda stupid. After all, we have [Poon-Dryja channels](https://en.bitcoin.it/wiki/Payment_channels#Poon-Dryja_payment_channels) that are powering the lightning network. They are bi-directional, do not expire, and can be used to shuffle coins back and forth theorethically an unlimited amount of times. So, why bother with this stupid one-way channel? ### Simplicity is king People that have worked with lightning channels can sing you a song about complexity, state handling and risks about the current state of bidirectional payment channels. Essentially, There are a lot of requirements on both channel parties when it comes to Liveness (being online) and also state handling (continuous backups).  In some cases, especially when in the context of end-users wanting to perform payments on their mobile phone, they would appreciate it if there was not so much complexity and overhead involved. The gist of the idea is to combine unidirectional channels and ecash mints to achieve the following: A self custodial unidirectional payment channel to an ecash mint, massively reducing the senders liveness and state handling requirements when compared to a lightning channel. Sending payments through the mint will be done through swapping some of the channel balance for ecash tokens. At this point, the user is trusting the mint to honor the redemption of these tokens, while the remaining channel balance remains in self custody. This gives them better controll over their funds than just holding their entire balance custodied in the mint. The ecash tokens can then be redeemed to pay a lightning invoice, just the same as it is done now with normal cashu mints.  So this channel, that has no liveness or state management requirements for the sender, and must have a pre-defined close time, seems to be a perfect fit for the following usecase: 1. A `sender` receives his salary once a month. He opens a channel that is valid for one month. 2. The `sender` then can do his daily spending over this channel. He only trusts the `mint` with the amount for the current outgoing payment while it is swapped for ecash, waiting for redemption. 3. If the `sender` must receive funds (a refund for example), he can do so into the `mints` custody, by receiving ecash. He can spend his ecash funds first when doing his next payment, to reduce his custodial exposure. 4. When the channel expires, or runs out of funds, the `mint` closes the channel. From a consumer perspective, that just want to receive his salary and make frequent payments afterwards, this usecase seems to make a lot of sense. Obviously from a merchants perspective on the other hand, such a channel doesn't really work. But that's fine, it's not the problem we're trying to solve here. What do you think of this idea? Be sure to let me know in the comments! In the next article, we will dive into how such a system can be implemented today, using Bitcoin, Cashu and Lightning. We will also discover how the system can be improved, to make channels non-expiring (A collaborative idea between nostr:npub148jz5r9xujcjpqygk69yl4jqwjqmzgrqly26plktfjy8g4t7xaysj9xhgp and nostr:npub1htnhsay5dmq3r72tukdw72pduzfdcja0yylcajuvnc2uklkhxp8qnz3qac born at nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx ). So stay tuned!
@ c4b5369a:b812dbd6
2025-02-12 12:23:40 ### Unidirectional payment channels revisited #### Nodeless lightning - Reduce ecash mints custodial risk --- ### Sats N Facts The nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx unconference has just wrapped up. And what a blast it was. In the heart of northern Thailand, developers, researchers, content creators and more, came together to share ideas on how Bitcoin, Nostr and other free protocols are being used everyday to liberate people. Not only were stories shared from different community leaders on how embracing bitcoin has empowered them and their communities, but a big goal of the unconference was to bring bitcoin engineers and developers from various domains together in one room, unstructured, chaotic, and let them do their thing. At first, I thought not having a schedule might be boring, but oh boy was I wrong. There was so much stuff going on, it was hard to choose which session I would have to miss! ### Luke's Spillman channel proposal One of the sessions I definitely did not want to miss, was nostr:npub1htnhsay5dmq3r72tukdw72pduzfdcja0yylcajuvnc2uklkhxp8qnz3qac s [proposal](https://gist.github.com/lukechilds/307341239beac72c9d8cfe3198f9bfff) > Ecash mints funded with Spillman channels: The ultimate nodeless Lightning wallet . In true unconference fashion, he announced in the main room that the session was about to start, and that the people that are interested should meet him in the whiteboard corner in 10 minutes. The corner was packed, and Luke explained his proposal. ### What's a "[Spillman channel](https://en.bitcoin.it/wiki/Payment_channels#Spillman-style_payment_channels)"? Essentially when we are talking about Spillman channels, what is meant are unidirectional payment channels (or [CLTV-style channels](https://en.bitcoin.it/wiki/Payment_channels#CLTV-style_payment_channels)). An unidirectional payment channel means, only one party can send payments, but not receive, and the other party can only receive, but not send. They also expire after a predetermined amount of time, and must be closed.  At first glance, this might look kinda stupid. After all, we have [Poon-Dryja channels](https://en.bitcoin.it/wiki/Payment_channels#Poon-Dryja_payment_channels) that are powering the lightning network. They are bi-directional, do not expire, and can be used to shuffle coins back and forth theorethically an unlimited amount of times. So, why bother with this stupid one-way channel? ### Simplicity is king People that have worked with lightning channels can sing you a song about complexity, state handling and risks about the current state of bidirectional payment channels. Essentially, There are a lot of requirements on both channel parties when it comes to Liveness (being online) and also state handling (continuous backups).  In some cases, especially when in the context of end-users wanting to perform payments on their mobile phone, they would appreciate it if there was not so much complexity and overhead involved. The gist of the idea is to combine unidirectional channels and ecash mints to achieve the following: A self custodial unidirectional payment channel to an ecash mint, massively reducing the senders liveness and state handling requirements when compared to a lightning channel. Sending payments through the mint will be done through swapping some of the channel balance for ecash tokens. At this point, the user is trusting the mint to honor the redemption of these tokens, while the remaining channel balance remains in self custody. This gives them better controll over their funds than just holding their entire balance custodied in the mint. The ecash tokens can then be redeemed to pay a lightning invoice, just the same as it is done now with normal cashu mints.  So this channel, that has no liveness or state management requirements for the sender, and must have a pre-defined close time, seems to be a perfect fit for the following usecase: 1. A `sender` receives his salary once a month. He opens a channel that is valid for one month. 2. The `sender` then can do his daily spending over this channel. He only trusts the `mint` with the amount for the current outgoing payment while it is swapped for ecash, waiting for redemption. 3. If the `sender` must receive funds (a refund for example), he can do so into the `mints` custody, by receiving ecash. He can spend his ecash funds first when doing his next payment, to reduce his custodial exposure. 4. When the channel expires, or runs out of funds, the `mint` closes the channel. From a consumer perspective, that just want to receive his salary and make frequent payments afterwards, this usecase seems to make a lot of sense. Obviously from a merchants perspective on the other hand, such a channel doesn't really work. But that's fine, it's not the problem we're trying to solve here. What do you think of this idea? Be sure to let me know in the comments! In the next article, we will dive into how such a system can be implemented today, using Bitcoin, Cashu and Lightning. We will also discover how the system can be improved, to make channels non-expiring (A collaborative idea between nostr:npub148jz5r9xujcjpqygk69yl4jqwjqmzgrqly26plktfjy8g4t7xaysj9xhgp and nostr:npub1htnhsay5dmq3r72tukdw72pduzfdcja0yylcajuvnc2uklkhxp8qnz3qac born at nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx ). So stay tuned! @ f3df9bc0:a95119eb
2025-01-03 21:36:45# MySql InnoDB Indexes for Developers This article aims to be a high level reference for developers who just want to use Mysql InnoDB indexes effectively. Although you _can_ read this from top to bottom, I'd encourage you to save time by skipping to sections that interest you using the below table of contents. # Contents - [Quick Reference](#quick-reference) (Start here for guidelines you can use right away, without needing the _why_) - [Index Structure](#index-structure) - [Primary Index Structure & Paging](#primary-index--paging) - [Secondary Indexes](#secondary-index-structure) - [Composite Indexes](#composite-index-structure) - [Index Navigation](#index-navigation) - [ref-type Queries](#ref-type-queries) - [range-type Queries](#range-type-queries) - [Post-Index Computations](#post-index-computations) - [Join Algorithms](#join-algorithms) - [Nested Loop Join](#nested-loop-join) - [Hash Join](#hash-join) - [Compound Cursor Iteration](#compound-cursor-iteration) <style type="text/css"> .box { background: #cedce8; padding: 1px 10px 5px 10px; border-radius: 15px; } .box code { background: #bfd7ec; } </style> <div class="box" style="" markdown="1"> # Quick Reference This is a quick list of the practical guidelines that you can use to make your applications more performant at the database layer. We'll dive into the _why_ each of these things are true, and give you mental models such that you can arrive at these guidelines yourself _without memorization_, at later sections of the article. <button onclick="toggle_quickref();">Click To Expand ▼</button> <script type="text/javascript"> function toggle_quickref() { var x = document.getElementById("quick-reference-body"); if (x.style.display === "none") { x.style.display = "block"; } else { x.style.display = "none"; } } </script> <div id="quick-reference-body" style="display:none" markdown="1"> **Structure** - Every non-`PRIMARY` index is really a compound index with the `PRIMARY` index. - `[foo]` is implicitly `[foo, id]`, likewise `[a, b]` is implicitly `[a, b, id]` - Usually prefer high cardinality columns (those with many unique values) to come earlier in indexes. - For example IDs have more unique values than boolean flags, so put the ID first in the index `[account_id, is_active]` - *Note:* there are exceptions, especially when range queries are involved - Only `SELECT`-ing columns contained in the index will significantly reduce memory paging. - eg `SELECT foo, id` when the index `[foo]` is being used. **Filtering** - An index must be "used" from left to right. Given an index of `[a, b, c]`: - 🟢 `WHERE b=2 AND a=1` will correctly use the `[a, b]` portion of the index - 🟡 `WHERE a=1 AND c=4` will only use the `[a]` portion of the index - 🔴 `WHERE b=5` will not be able to use this index at all - A range filter prevents any columns to the "right" from being used. Given an index of `[a, b, c]`: - 🟡 `WHERE a=1 AND b>4 AND c=10` will only use the `[a, b]` portion of the index - 🔴 Implied by this is that queries containing ranges on two or more columns **cannot** be solved by indexes `WHERE a>5 AND b>2` - Any filters that aren't solved as part of the index will require linear row scanning. The performance of this is correlated to the "hit ratio". - Given an index of `[a]`, the performance of `WHERE a=1 AND c=4` will correlate to *what percentage of `a=1` rows also have `c=4`*. If this percentage is low, performance will be worse. Put another way: if there are a large number of rows where `a=1` but only a couple of those also have `c=4`, mysql will need to search through and discard many rows. **Ordering** - Indexes naturally return rows ordered by their structure. - Selecting from index `[a, b]` will naturally give rows ordered by `[a, b, id]` - Any unnatural ordering will require a O(nlogn) **filesort**, which can be very slow for large amounts of rows - With an index of `[a]`, the query `WHERE a=1 ORDER BY b` will need to sort all rows that meet the filtering clause. - Columns on the "left" of the index can be efficiently excluded from the `ORDER BY` clause, **if** they have been used in the `WHERE` clause as a **non-range** filter. - Given an index of `[a, b]`, with a natural ordering of `[a, b, id]`: - 🟢 `WHERE a=1 ORDER BY b,id` is also natural ordering - 🔴 `WHERE a=1 ORDER BY id` is **not** natural ordering - 🟢 `WHERE a=1 AND b>10 ORDER BY b,id` is natural ordering - 🔴 `WHERE a=1 AND b>10 ORDER BY id` is **not** natural ordering - 🟢 `WHERE a=1 AND b=2 ORDER BY id` is natural ordering - 🟢 `WHERE a=1 AND b=2 AND id>5 ORDER BY id` is natural ordering **Limit & Offset** - Performance of `LIMIT` is correlated to the "hit density" when scanning rows. eg are the rows you're scanning for abundant? Or will mysql need to scan for a long time to find enough rows? - `LIMIT` is applied **after** sorting, so will not improve the performance of a filesort - Performance of `OFFSET n` is correclated to the value of `n`. Therefore it is not a good fit for pagination as the query will get slower as `n` increases. </div> </div> ----- # Index Structure Indexes are constructed from a B+tree structure. Understanding this structure is key to gaining an intuitive reasoning for how queries will perform using different indexes. Both the `PRIMARY` index and secondary indexes have a similar tree structure, differing only in what data is stored on the leaves of the tree. ## Primary Index Structure & Paging Looking at the structure of a `PRIMARY` index first, we see that the full row is stored in each leaf of the tree, and each leaf is ordered sequentially on the disk:  <center><small style="color: #999">note: page size greatly reduced for illustration</small></center> If possible, it is best to select the primary index for a table with data locality in mind, to reduce how many page loads need to take place to satisfy a query. For example, imagine a blogging application that almost always queries for posts on a specific blog: `SELECT * FROM posts WHERE blog_id=10`. Ideally we'd like for this table to have all the posts where `blog_id = 10` stored **sequentially** in the primary index. However, by using a standard primary index on `[id]` we see a structure where rows are stored in disk pages in the order they were **created**. The diagram below illistrates this (ID integer, colour coded by blog)  By insteading using a **composite primary key**, this table can be made much more efficient given its access pattern. In the below diagram I show the same data, but instead stored in a composite primary index of `[blog_id, id]`. This means rows are first sorted by `blog_id`, and then by `id` for each blog. When the data is stored in this manner, our query for `SELECT * FROM posts WHERE blog_id=10` is likely to load less pages from disk.  ## Secondary Index Structure Secondary indexes have a similar structure to that of primary indexes. However, instead of storing the _full row_ in the leaves of the tree, only the primary index value is stored:  This structure means that if additional columns are required (eg a `SELECT *`), then after traversing the secondary index, mysql must also traverse the primary index _for each selected row_ to actually load the required data. By only selecting columns available in the secondary index, mysql can skip this extra lookup step. ## Composite Index Structure When multiple columns are specified in a compound index, we get a structure composed of **nested B+trees**. This is where the ordering of columns within an index definition becomes relevant. The root of the tree is defined by the _first_ column in the index definition, the second nested tree would be the _second_ column in the index definition, and so on. The below diagram is the structure of a composite index `[blog_id, created_at]` (with the implied `id` column on the end):  # Index Navigation We'll now look at how mysql navigates these indexes given various query structures, which should help give an intuitive understanding for why Mysql performance will vary. ## `ref`-type queries With this tree-based model in place, we can see that to efficiently use an index like this we must navigate the tree _in the order that the index is defined_. If our query does not specify a value for all columns in an index, this is ok as long as the values we _do_ provide are at the top of the tree. I've illustrated below two examples of the "happy path" for navigating a `[blog_id, user_id]` index. In the first, we have provided a filter on both `blog_id` and `user_id`, which allows for mysql to fully navigate the tree to the leaves. In the second, we only provide a filter on `blog_id`, but because this is the first column in the index mysql is still able to efficiently select all the rows that meet this criteria (it selects **all leaves from the sub tree**)  <div class="box" style="" markdown="1"> 💡 Notice how the ordering of the rows appears to change depending on **how far mysql navigates the tree**. Rows in an index are always stored in the same ordering scheme as the index itself. That is to say that a `[blog_id, user_id]` index will naturally store rows in `blog_id, user_id, id` ordering. However, as we navigate further into the tree the ordering appears to "simplify". If we are selecting rows for a specific `blog=10 and user_id=50` then the rows appear to be ordered by `id`, because they all share the same values for both blog_id and user_id! </div> ## `range`-type queries The range-type lookup happens when a query selects _multiple values_ for an indexed column. There are many ways a query could end up in this scenario: - `WHERE updated_at > X` - `WHERE user_id != X` - `WHERE blog_id IN (1, 5, 34, 200)` - `WHERE user_id=10 OR user_id=50` In such cases, mysql will need to navigate _multiple branches_ of the index. Consider the below query where we search for all recently created posts for a particular blog:  There are two things I'd like to point out about this pattern: 1. The ordering of the results is `created_at, id`. Sorting by `id` (for example) is not possible without a `filesort` operation. 2. There is no efficient way to navigate the deeper sections of the tree (ie the `id` portion of the index above) without iterating through all the selected branches of `created_at`. That is, if we were to add an additional filter on `id > 5` for example, then there is no single tree to navigate and provide these values. Mysql would instead need to iterate through every sub-tree (one per value of `created_at`) to complete this filtering operation (see diagram below) A common application pattern that can suffer performance issues due to both these points is *ID-based pagination* (ie if your pagination system needs to filter on `WHERE id > x ORDER BY id`). See the section on [compound cursor iteration](#compound-cursor-iteration) for a potential solution.  # Post-Index Computations Although Mysql will always start off by using an index if possible to reduce the amount of post-processing required, it goes without saying that not every query will be fully solved by an avilable index. There are a couple post-index computations that we should consider the relative performance of. First, if the query is requesting an `ORDER` which differs from how the index sorts its rows, a filesort will be required. This is an expensive operation (`O(nlogn)`) if the number of rows to be sorted is large. In addition, sorting requires Mysql to temporarily buffer the entire dataset (eg you can't stream a sorting operation). See [ref-type queries](#ref-type-queries) for a reminder how indexes naturally sort rows. If the `WHERE` clause of the query was not fully solved by the index, Mysql will also need to scan through the rows one after another to apply the remaining filtering. While this is faster than a filesort, it is also relatively slow for large data sets (`O(n)`). If the index reducing the dataset down to a reasonable size upfront, then this may not be a big deal.  There is one exception here: if the query also specifies a `LIMIT x`, Mysql need not scan the _entire_ dataset. Mysql will "short circuit" the row scan as soon as it has enough rows to satisfy the query condition. The performance of this kind of pattern is dependent on the "hit ratio" of rows. If there are relatively few rows that satisfy the filter condition compared to rows that must be dropped, then Mysql will need to scan for a longer time compared to if almost all the rows are valid. In addition, you may find that the "density" of interesting rows is not constant throughout the range being scanned! If your application is paginating through a large data set, you may find that different pages have different query times, depending on how many rows need to be filtered out on each page.  # Join Algorithms ## Nested-Loop Join The primary algorithm used by Mysql to join tables is a couple variations on "nested-loop". This a very straightforward algorithm: ``` for each row in tableA: for each matching row in tableB: send to output steram ``` Because Mysql is often capable of streaming joins, when the join query includes a `LIMIT x` the full join may not have to be executed: 1. Mysql executes query in the outer table 2. For the first row in the range, look-up matching rows in the inner table 3. For each matching row, emit to output stream 4. Stop execution if enough rows found, otherwise move to next row and goto 2 Note that similar to un-indexed row scans, this does not apply to all conditions (for example, if sorting is required the full dataset is required in memory). ## Hash Join The hash-join algorithm avoids the N+1 B-tree traversal by taking some time upfront (`O(n)`) to build an in-memory hash table. The reason this strategy can give a performance improvement over nested-loop in some cases is because a hash table lookup has an average profile of `O(1)` compared to B-tree traversal at `O(logn)`. Given we may have to do this lookup many times (`m` times), the overall performance profile of hash-join is `O(n + m)`, whereas nested-loop's profile is `O(nlogm)`. The below plot shows the region (shaded blue) where the function `n+m` has a lower value than `n*logm`:  The tradeoff is of course that this (potentially large) hash table must fit into memory. For this reason one strategy to improve hash-join performance is to limit the size of this temporary table by `SELECT`-ing only those columns which you really need (to reduce width), and pre-filtering as many rows as possible (to reduce height). The second thing to keep in mind for performance of hash-joins is that indexes on the join condition will not be used. Rather, the place to focus is on indexing any independent filters if possible. For example, consider the following query: ```sql SELECT * FROM tableA t1 JOIN tableB t2 ON t1.shared_id = t2.shared_id WHERE t1.colA = "foo" AND t2.colB = "bar" ``` The best indexes for this query given a hash-join would be on `t1.colA` and a second index on `t2.colB`. Execution of this join would then look like: 1. Use the index on `colA` to find all rows in t1 where `colA = "foo"`. 2. For each row, build a hash table where the key is `t1.shared_id` and the value is the row. 3. Use the index on `colB` to find all rows in t2 where `colB = "bar"`. 4. For each row, look up the matching t1 rows from the hash table by `t2.shared_id` # Compound Cursor Iteration In the [range-type queries section](#range-type-queries) I briefly introduced the problem of using an ID based cursor to paginate through a dataset queried via a range-type query. One potential solution to this problem is to use a *compound cursor*. To work, this cursor must be constructed from the column being filtered with the range. For example, lets consider the query `SELECT * FROM blog_posts WHERE blog_id=10 AND created_at>"2023-01-01"`. The natural index to use for this range query would be `[blog_id, created_at]`. Because the range query filter is performed on the `created_at` column, I will propose a compound cursor of `created_at, id`. Let's take a look at how the query structure changes. The first query of our iteration will look something like this: ```sql SELECT * FROM blog_posts WHERE blog_id = 10 AND created_at > "2023-01-01" ORDER BY created_at, id ASC LIMIT 100 ``` This will get the first "page" of 100 results. Notice that we are ordering by `created_at, id`, which is the natural ordering of the index. This allows mysql to efficiently grab the first 100 rows it sees without scanning the full time range.  Now lets look at how we get the next "page" of results. The "cursor value" is defined as the `created_at` and `id` values from the last row in the batch of 100 previously selected. We'll call these values `x` and `y` for simplicity. ```ruby x = batch.last.created_at, y = batch.last.id ``` The structure of the query that loads the second page of results has this form: ```sql SELECT * FROM blog_posts WHERE blog_id = 10 AND ( created_at = x AND id > y OR created_at > x ) ORDER BY created_at, id ASC LIMIT 100 ``` Notice in this query that we have an `OR` clause, meaning mysql is going to navigate the index **two times**, once per "side" of the clause. Lets consider these as two seperate queries for the sake of a performance analysis. ```sql -- Query A: the "left" side of the OR clause SELECT * FROM blog_posts WHERE blog_id = 10 AND created_at = x AND id > y ORDER BY created_at, id ASC LIMIT 100 -- Query B: the "right" side of the OR clause SELECT * FROM blog_posts WHERE blog_id = 10 AND created_at > x ORDER BY created_at, id ASC LIMIT 100 ``` By analysing the OR clauses piece-wise like this, we can now see that each clause has only **one** range filter. Combining this with the fact that the `ORDER BY` is the natural ordering of these indexes, we have solved both of the original problems! No more filesort, no more unsolvable double-range filters.  🟡 A note of warning: this pattern may only work as you expect for columns that have **immutable** values. Like any data structure iteration, if a value changes during your iteration your process may either process a row twice or not at all! For example, consider if instead of iterating on `created_at, id` we were iterating on `updated_at, id`. If a row is updated (and therefore `updated_at` _increases_) while a process is already iterating through the dataset, we may see that updated row twice: once with its lower `updated_at` value, and again with the higher value.
@ f3df9bc0:a95119eb
2025-01-03 21:36:45# MySql InnoDB Indexes for Developers This article aims to be a high level reference for developers who just want to use Mysql InnoDB indexes effectively. Although you _can_ read this from top to bottom, I'd encourage you to save time by skipping to sections that interest you using the below table of contents. # Contents - [Quick Reference](#quick-reference) (Start here for guidelines you can use right away, without needing the _why_) - [Index Structure](#index-structure) - [Primary Index Structure & Paging](#primary-index--paging) - [Secondary Indexes](#secondary-index-structure) - [Composite Indexes](#composite-index-structure) - [Index Navigation](#index-navigation) - [ref-type Queries](#ref-type-queries) - [range-type Queries](#range-type-queries) - [Post-Index Computations](#post-index-computations) - [Join Algorithms](#join-algorithms) - [Nested Loop Join](#nested-loop-join) - [Hash Join](#hash-join) - [Compound Cursor Iteration](#compound-cursor-iteration) <style type="text/css"> .box { background: #cedce8; padding: 1px 10px 5px 10px; border-radius: 15px; } .box code { background: #bfd7ec; } </style> <div class="box" style="" markdown="1"> # Quick Reference This is a quick list of the practical guidelines that you can use to make your applications more performant at the database layer. We'll dive into the _why_ each of these things are true, and give you mental models such that you can arrive at these guidelines yourself _without memorization_, at later sections of the article. <button onclick="toggle_quickref();">Click To Expand ▼</button> <script type="text/javascript"> function toggle_quickref() { var x = document.getElementById("quick-reference-body"); if (x.style.display === "none") { x.style.display = "block"; } else { x.style.display = "none"; } } </script> <div id="quick-reference-body" style="display:none" markdown="1"> **Structure** - Every non-`PRIMARY` index is really a compound index with the `PRIMARY` index. - `[foo]` is implicitly `[foo, id]`, likewise `[a, b]` is implicitly `[a, b, id]` - Usually prefer high cardinality columns (those with many unique values) to come earlier in indexes. - For example IDs have more unique values than boolean flags, so put the ID first in the index `[account_id, is_active]` - *Note:* there are exceptions, especially when range queries are involved - Only `SELECT`-ing columns contained in the index will significantly reduce memory paging. - eg `SELECT foo, id` when the index `[foo]` is being used. **Filtering** - An index must be "used" from left to right. Given an index of `[a, b, c]`: - 🟢 `WHERE b=2 AND a=1` will correctly use the `[a, b]` portion of the index - 🟡 `WHERE a=1 AND c=4` will only use the `[a]` portion of the index - 🔴 `WHERE b=5` will not be able to use this index at all - A range filter prevents any columns to the "right" from being used. Given an index of `[a, b, c]`: - 🟡 `WHERE a=1 AND b>4 AND c=10` will only use the `[a, b]` portion of the index - 🔴 Implied by this is that queries containing ranges on two or more columns **cannot** be solved by indexes `WHERE a>5 AND b>2` - Any filters that aren't solved as part of the index will require linear row scanning. The performance of this is correlated to the "hit ratio". - Given an index of `[a]`, the performance of `WHERE a=1 AND c=4` will correlate to *what percentage of `a=1` rows also have `c=4`*. If this percentage is low, performance will be worse. Put another way: if there are a large number of rows where `a=1` but only a couple of those also have `c=4`, mysql will need to search through and discard many rows. **Ordering** - Indexes naturally return rows ordered by their structure. - Selecting from index `[a, b]` will naturally give rows ordered by `[a, b, id]` - Any unnatural ordering will require a O(nlogn) **filesort**, which can be very slow for large amounts of rows - With an index of `[a]`, the query `WHERE a=1 ORDER BY b` will need to sort all rows that meet the filtering clause. - Columns on the "left" of the index can be efficiently excluded from the `ORDER BY` clause, **if** they have been used in the `WHERE` clause as a **non-range** filter. - Given an index of `[a, b]`, with a natural ordering of `[a, b, id]`: - 🟢 `WHERE a=1 ORDER BY b,id` is also natural ordering - 🔴 `WHERE a=1 ORDER BY id` is **not** natural ordering - 🟢 `WHERE a=1 AND b>10 ORDER BY b,id` is natural ordering - 🔴 `WHERE a=1 AND b>10 ORDER BY id` is **not** natural ordering - 🟢 `WHERE a=1 AND b=2 ORDER BY id` is natural ordering - 🟢 `WHERE a=1 AND b=2 AND id>5 ORDER BY id` is natural ordering **Limit & Offset** - Performance of `LIMIT` is correlated to the "hit density" when scanning rows. eg are the rows you're scanning for abundant? Or will mysql need to scan for a long time to find enough rows? - `LIMIT` is applied **after** sorting, so will not improve the performance of a filesort - Performance of `OFFSET n` is correclated to the value of `n`. Therefore it is not a good fit for pagination as the query will get slower as `n` increases. </div> </div> ----- # Index Structure Indexes are constructed from a B+tree structure. Understanding this structure is key to gaining an intuitive reasoning for how queries will perform using different indexes. Both the `PRIMARY` index and secondary indexes have a similar tree structure, differing only in what data is stored on the leaves of the tree. ## Primary Index Structure & Paging Looking at the structure of a `PRIMARY` index first, we see that the full row is stored in each leaf of the tree, and each leaf is ordered sequentially on the disk:  <center><small style="color: #999">note: page size greatly reduced for illustration</small></center> If possible, it is best to select the primary index for a table with data locality in mind, to reduce how many page loads need to take place to satisfy a query. For example, imagine a blogging application that almost always queries for posts on a specific blog: `SELECT * FROM posts WHERE blog_id=10`. Ideally we'd like for this table to have all the posts where `blog_id = 10` stored **sequentially** in the primary index. However, by using a standard primary index on `[id]` we see a structure where rows are stored in disk pages in the order they were **created**. The diagram below illistrates this (ID integer, colour coded by blog)  By insteading using a **composite primary key**, this table can be made much more efficient given its access pattern. In the below diagram I show the same data, but instead stored in a composite primary index of `[blog_id, id]`. This means rows are first sorted by `blog_id`, and then by `id` for each blog. When the data is stored in this manner, our query for `SELECT * FROM posts WHERE blog_id=10` is likely to load less pages from disk.  ## Secondary Index Structure Secondary indexes have a similar structure to that of primary indexes. However, instead of storing the _full row_ in the leaves of the tree, only the primary index value is stored:  This structure means that if additional columns are required (eg a `SELECT *`), then after traversing the secondary index, mysql must also traverse the primary index _for each selected row_ to actually load the required data. By only selecting columns available in the secondary index, mysql can skip this extra lookup step. ## Composite Index Structure When multiple columns are specified in a compound index, we get a structure composed of **nested B+trees**. This is where the ordering of columns within an index definition becomes relevant. The root of the tree is defined by the _first_ column in the index definition, the second nested tree would be the _second_ column in the index definition, and so on. The below diagram is the structure of a composite index `[blog_id, created_at]` (with the implied `id` column on the end):  # Index Navigation We'll now look at how mysql navigates these indexes given various query structures, which should help give an intuitive understanding for why Mysql performance will vary. ## `ref`-type queries With this tree-based model in place, we can see that to efficiently use an index like this we must navigate the tree _in the order that the index is defined_. If our query does not specify a value for all columns in an index, this is ok as long as the values we _do_ provide are at the top of the tree. I've illustrated below two examples of the "happy path" for navigating a `[blog_id, user_id]` index. In the first, we have provided a filter on both `blog_id` and `user_id`, which allows for mysql to fully navigate the tree to the leaves. In the second, we only provide a filter on `blog_id`, but because this is the first column in the index mysql is still able to efficiently select all the rows that meet this criteria (it selects **all leaves from the sub tree**)  <div class="box" style="" markdown="1"> 💡 Notice how the ordering of the rows appears to change depending on **how far mysql navigates the tree**. Rows in an index are always stored in the same ordering scheme as the index itself. That is to say that a `[blog_id, user_id]` index will naturally store rows in `blog_id, user_id, id` ordering. However, as we navigate further into the tree the ordering appears to "simplify". If we are selecting rows for a specific `blog=10 and user_id=50` then the rows appear to be ordered by `id`, because they all share the same values for both blog_id and user_id! </div> ## `range`-type queries The range-type lookup happens when a query selects _multiple values_ for an indexed column. There are many ways a query could end up in this scenario: - `WHERE updated_at > X` - `WHERE user_id != X` - `WHERE blog_id IN (1, 5, 34, 200)` - `WHERE user_id=10 OR user_id=50` In such cases, mysql will need to navigate _multiple branches_ of the index. Consider the below query where we search for all recently created posts for a particular blog:  There are two things I'd like to point out about this pattern: 1. The ordering of the results is `created_at, id`. Sorting by `id` (for example) is not possible without a `filesort` operation. 2. There is no efficient way to navigate the deeper sections of the tree (ie the `id` portion of the index above) without iterating through all the selected branches of `created_at`. That is, if we were to add an additional filter on `id > 5` for example, then there is no single tree to navigate and provide these values. Mysql would instead need to iterate through every sub-tree (one per value of `created_at`) to complete this filtering operation (see diagram below) A common application pattern that can suffer performance issues due to both these points is *ID-based pagination* (ie if your pagination system needs to filter on `WHERE id > x ORDER BY id`). See the section on [compound cursor iteration](#compound-cursor-iteration) for a potential solution.  # Post-Index Computations Although Mysql will always start off by using an index if possible to reduce the amount of post-processing required, it goes without saying that not every query will be fully solved by an avilable index. There are a couple post-index computations that we should consider the relative performance of. First, if the query is requesting an `ORDER` which differs from how the index sorts its rows, a filesort will be required. This is an expensive operation (`O(nlogn)`) if the number of rows to be sorted is large. In addition, sorting requires Mysql to temporarily buffer the entire dataset (eg you can't stream a sorting operation). See [ref-type queries](#ref-type-queries) for a reminder how indexes naturally sort rows. If the `WHERE` clause of the query was not fully solved by the index, Mysql will also need to scan through the rows one after another to apply the remaining filtering. While this is faster than a filesort, it is also relatively slow for large data sets (`O(n)`). If the index reducing the dataset down to a reasonable size upfront, then this may not be a big deal.  There is one exception here: if the query also specifies a `LIMIT x`, Mysql need not scan the _entire_ dataset. Mysql will "short circuit" the row scan as soon as it has enough rows to satisfy the query condition. The performance of this kind of pattern is dependent on the "hit ratio" of rows. If there are relatively few rows that satisfy the filter condition compared to rows that must be dropped, then Mysql will need to scan for a longer time compared to if almost all the rows are valid. In addition, you may find that the "density" of interesting rows is not constant throughout the range being scanned! If your application is paginating through a large data set, you may find that different pages have different query times, depending on how many rows need to be filtered out on each page.  # Join Algorithms ## Nested-Loop Join The primary algorithm used by Mysql to join tables is a couple variations on "nested-loop". This a very straightforward algorithm: ``` for each row in tableA: for each matching row in tableB: send to output steram ``` Because Mysql is often capable of streaming joins, when the join query includes a `LIMIT x` the full join may not have to be executed: 1. Mysql executes query in the outer table 2. For the first row in the range, look-up matching rows in the inner table 3. For each matching row, emit to output stream 4. Stop execution if enough rows found, otherwise move to next row and goto 2 Note that similar to un-indexed row scans, this does not apply to all conditions (for example, if sorting is required the full dataset is required in memory). ## Hash Join The hash-join algorithm avoids the N+1 B-tree traversal by taking some time upfront (`O(n)`) to build an in-memory hash table. The reason this strategy can give a performance improvement over nested-loop in some cases is because a hash table lookup has an average profile of `O(1)` compared to B-tree traversal at `O(logn)`. Given we may have to do this lookup many times (`m` times), the overall performance profile of hash-join is `O(n + m)`, whereas nested-loop's profile is `O(nlogm)`. The below plot shows the region (shaded blue) where the function `n+m` has a lower value than `n*logm`:  The tradeoff is of course that this (potentially large) hash table must fit into memory. For this reason one strategy to improve hash-join performance is to limit the size of this temporary table by `SELECT`-ing only those columns which you really need (to reduce width), and pre-filtering as many rows as possible (to reduce height). The second thing to keep in mind for performance of hash-joins is that indexes on the join condition will not be used. Rather, the place to focus is on indexing any independent filters if possible. For example, consider the following query: ```sql SELECT * FROM tableA t1 JOIN tableB t2 ON t1.shared_id = t2.shared_id WHERE t1.colA = "foo" AND t2.colB = "bar" ``` The best indexes for this query given a hash-join would be on `t1.colA` and a second index on `t2.colB`. Execution of this join would then look like: 1. Use the index on `colA` to find all rows in t1 where `colA = "foo"`. 2. For each row, build a hash table where the key is `t1.shared_id` and the value is the row. 3. Use the index on `colB` to find all rows in t2 where `colB = "bar"`. 4. For each row, look up the matching t1 rows from the hash table by `t2.shared_id` # Compound Cursor Iteration In the [range-type queries section](#range-type-queries) I briefly introduced the problem of using an ID based cursor to paginate through a dataset queried via a range-type query. One potential solution to this problem is to use a *compound cursor*. To work, this cursor must be constructed from the column being filtered with the range. For example, lets consider the query `SELECT * FROM blog_posts WHERE blog_id=10 AND created_at>"2023-01-01"`. The natural index to use for this range query would be `[blog_id, created_at]`. Because the range query filter is performed on the `created_at` column, I will propose a compound cursor of `created_at, id`. Let's take a look at how the query structure changes. The first query of our iteration will look something like this: ```sql SELECT * FROM blog_posts WHERE blog_id = 10 AND created_at > "2023-01-01" ORDER BY created_at, id ASC LIMIT 100 ``` This will get the first "page" of 100 results. Notice that we are ordering by `created_at, id`, which is the natural ordering of the index. This allows mysql to efficiently grab the first 100 rows it sees without scanning the full time range.  Now lets look at how we get the next "page" of results. The "cursor value" is defined as the `created_at` and `id` values from the last row in the batch of 100 previously selected. We'll call these values `x` and `y` for simplicity. ```ruby x = batch.last.created_at, y = batch.last.id ``` The structure of the query that loads the second page of results has this form: ```sql SELECT * FROM blog_posts WHERE blog_id = 10 AND ( created_at = x AND id > y OR created_at > x ) ORDER BY created_at, id ASC LIMIT 100 ``` Notice in this query that we have an `OR` clause, meaning mysql is going to navigate the index **two times**, once per "side" of the clause. Lets consider these as two seperate queries for the sake of a performance analysis. ```sql -- Query A: the "left" side of the OR clause SELECT * FROM blog_posts WHERE blog_id = 10 AND created_at = x AND id > y ORDER BY created_at, id ASC LIMIT 100 -- Query B: the "right" side of the OR clause SELECT * FROM blog_posts WHERE blog_id = 10 AND created_at > x ORDER BY created_at, id ASC LIMIT 100 ``` By analysing the OR clauses piece-wise like this, we can now see that each clause has only **one** range filter. Combining this with the fact that the `ORDER BY` is the natural ordering of these indexes, we have solved both of the original problems! No more filesort, no more unsolvable double-range filters.  🟡 A note of warning: this pattern may only work as you expect for columns that have **immutable** values. Like any data structure iteration, if a value changes during your iteration your process may either process a row twice or not at all! For example, consider if instead of iterating on `created_at, id` we were iterating on `updated_at, id`. If a row is updated (and therefore `updated_at` _increases_) while a process is already iterating through the dataset, we may see that updated row twice: once with its lower `updated_at` value, and again with the higher value. @ c2827524:5f45b2f7
2025-02-12 12:22:11## L’animo umano  Una delle entità più belle che esistono e che, a mio parere, rendono ancor più meraviglioso questo mondo, è **l’animo degli esseri umani**. È un cocktail fatto di sentimenti, intenzioni, azioni e logica. Quelli che preferisco sono gli animi gentili. Le azioni e le intenzioni devono convergere verso la delicatezza, senza una sbavatura, per essere gentili e io adoro la gentilezza, la riconosco al volo, forse perché non sono delicata. Per niente. L’animo è forse **uno dei più grandi segreti dell’umanità**: in genere perché lo si tiene sempre privato, come è anche logico che sia. C’è un solo fattore che fa rivelare l’animo alle persone, loro malgrado: uno stress test estremo. Dal febbraio del 2020, lo stress test si è tramutato in un organismo multidimensionale, uscendo dalla fantasia distopica di George Orwell e – loro malgrado – **tutti hanno dovuto manifestare l’animo segreto**. Fateci caso: è con il covid-1984 che avete scoperto la vera natura di amici, parenti, sconosciuti o conoscenti. ## Stato di eccezione  La distopia non è mica fuoriuscita da un laboratorio di Wuhan, che ha infettato un pangolino, che ha infettato una papera, che al mercato mio padre comprò. **Ha origini molto più antiche**. Profondi conoscitori dell’animo umano, in grado di prevedere le reazioni delle masse di fronte ad ogni tipo di evento, potrebbero progettare modelli catastrofici e predeterminare con una precisione disarmante la risposta delle persone comuni. Ad esempio di fronte alla probabilità che quattro aerei impazziscano nei cieli americani di una splendida mattina di settembre, oppure guardando i corpi smembrati di un attentato compiuto da una qualunque “sigla” islamica. Infine, potrebbero decidere come e quando dare una sferzata finale allo stress test, ad esempio con il pangolino. O era il pipistrello? È la *«forma legale di ciò che non può avere forma legale»*, più in generale lo spirito disumano dei governanti di oggi, la consuetudine della guerra preventiva, la quale impone con forza che *«lo stato di eccezione tende sempre più a presentarsi come il paradigma di governo dominante della politica contemporanea»*. Così analizza magistralmente Giorgio Agamben nel II° volume della raccolta Homo Sacer, intitolato per l’appunto [Stato di Eccezione](https://www.amazon.it/s?k=stato+di+eccezione+agamben&adgrpid=1234751876426057&hvadid=77172156923137&hvbmt=be&hvdev=c&hvlocphy=1861&hvnetw=s&hvqmt=e&hvtargid=kwd-77172234261086%3Aloc-93&hydadcr=18605_1867270&mcid=df58fe78258f374b81f1fd0eeaa1c659&msclkid=ea580711f461117b4cc160bdad34d584&tag=amamitsp-21&ref=pd_sl_7ni9dvsw1h_e). ## Stato indegno  Gli esseri umani, fondamentalmente miti e pacifici, tendono a condurre vite “normali” in ogni condizione ambientale. Un’unica variabile tende ad interferire per cambiare la condizione ambientale: la politica dello stato. E **lo fa in maniera sempre negativa**. Lo stato crea emergenze, per poi sbattere il suo (piccolissimo) pene sul tavolo e imporre con forza la soluzione, che tenderà puntualmente a facilitare la propria vita rendendo impossibile quella dei ~~cittadini~~ sudditi. Le disuguaglianze create hanno poi **il solo scopo di mettere** esseri miti e pacifici (ma sotto costante pressione) **gli uni contro gli altri**. Pensateci: da quanti decenni siete sotto la pressione di una *«forma legale di ciò che non può avere forma legale»*? Sentendo il Marchese del Grillo ***«Io so’ io, voi siete un cazzo»***, probabilmente è qualche secolo che questo stato indegno esiste. ## Vera natura o Nuda vita?  Il fatto, poi, che lo stato indegno venga accettato senza fiatare, fa parte di quella serie di reazioni delle masse e che i profondi conoscitori dell’animo umano sfruttano per mantenere il potere. Si passa poi alle peggiori angherie che lo stato indegno e i suoi agenti perpetrano nei confronti dei ~~cittadini~~ sudditi, alle estreme disparità tra ~~cittadini~~ sudditi e i “servitori” dello stato, chiamati così perché servono lo stato indegno e non i ~~cittadini~~ sudditi. Prima di arrivare alla sferzata finale dello stress test, persone miti e pacifiche hanno subito così tanti torti da non saperli più contare, ormai fanno parte della normalità. La loro esistenza è ormai ridotta a quello che Walter Benjamin prima e Giorgio Agamben poi definiscono la **Nuda Vita**, mettendo in analogia i sudditi con i detenuti di Guantanamo, giuridicamente innominabili e inclassificabili, ovvero ***«oggetto di una pura signoria di fatto»***. ## Il sontuoso master  Nello stato di eccezione in cui viviamo da almeno 50 anni, a parte pochi dotati di un immenso spirito di osservazione (e i profondi conoscitori al potere, chiaro), nessuno di noi ha mai avuto **veramente** il piacere di conoscere la reale natura delle persone con cui abbiamo scelto di circondarci. Magari c’era quel “piccolo tarlo”, quella “vocina” che ci ha fatto preferire alcuni piuttosto che altri, ma alla fine ha sempre prevalso l’attitudine mite e pacifica, che ha messo a tacere quella vocina. covid-1984 ha il merito di aver messo a nudo tutti: vittime e carnefici. Si tratta verosimilmente di **un sontuoso master che svelerà la vera natura di ognuno**, **nessuno escluso**. Ahinoi, il master è decennale e siamo appena all'inizio del V° anno accademico. ## Istruzioni, prima ancora che l’istruzione  Se c’è un consiglio che mi sento di dare a chi è ancora molto giovane, è proprio quello di non mettere mai a tacere quella “vocina”, per nessun motivo, seppure plausibile. Anche senza rovinare i rapporti, ma l’animo umano va sempre indagato, **si deve fare chiarezza sulla vera natura delle persone con cui si decide di fare un percorso di vita**. La scoperta porterà ad evitare tutti quei “servitori” dello stato di cose indegno di essere definito umano. I *compliant*, gli asserviti, quelli senza spina dorsale o, peggio, **che hanno un interesse personale a mantenere lo status quo** devono essere evitati a tutti i costi. È oltremodo doloroso, ma va fatto. Questi indegni devono essere isolati al più presto, in maniera da renderli innocui. Sono loro il vero esercito dello stato indegno, disposti a combattere qualunque guerra pur di rimediare un piccolissimo quanto ridicolo privilegio. Oggi, i tempi in cui questo esercito si abbassava a tanto per il classico piatto di lenticchie riscaldate, sono un lontanissimo ricordo. covid-1984 ha ulteriormente abbattuto lo standard: ora gli indegni fiancheggiano qualsiasi assurdità **in cambio di un piatto di lenticchie rimasticate dalla signoria di fatto**. L’unico risultato possibile è che l'infame stato rafforza il suo potere di controllo e rosicherà uno alla volta i (pochi) diritti e la libertà di chiunque. Ecco perché bisogna spuntare le armi di questo spregevole stato di cose colpendo l’anello debole, isolandolo. Debole perché non ci crede (nello stato) ma agisce asservito solo per quel piatto di lenticchie (quelle rimasticate e sputate). La prima volta che si incontrano, la vocina vi metterà di fronte alla sensazione di essere ai limiti di uno scontro frontale: capire da che parte andrà il rivale, per buttarsi in quella opposta ed evitare così uno schianto fatale. Fatelo: buttatevi dall’altra parte. E scegliete la parte giusta.
@ c2827524:5f45b2f7
2025-02-12 12:22:11## L’animo umano  Una delle entità più belle che esistono e che, a mio parere, rendono ancor più meraviglioso questo mondo, è **l’animo degli esseri umani**. È un cocktail fatto di sentimenti, intenzioni, azioni e logica. Quelli che preferisco sono gli animi gentili. Le azioni e le intenzioni devono convergere verso la delicatezza, senza una sbavatura, per essere gentili e io adoro la gentilezza, la riconosco al volo, forse perché non sono delicata. Per niente. L’animo è forse **uno dei più grandi segreti dell’umanità**: in genere perché lo si tiene sempre privato, come è anche logico che sia. C’è un solo fattore che fa rivelare l’animo alle persone, loro malgrado: uno stress test estremo. Dal febbraio del 2020, lo stress test si è tramutato in un organismo multidimensionale, uscendo dalla fantasia distopica di George Orwell e – loro malgrado – **tutti hanno dovuto manifestare l’animo segreto**. Fateci caso: è con il covid-1984 che avete scoperto la vera natura di amici, parenti, sconosciuti o conoscenti. ## Stato di eccezione  La distopia non è mica fuoriuscita da un laboratorio di Wuhan, che ha infettato un pangolino, che ha infettato una papera, che al mercato mio padre comprò. **Ha origini molto più antiche**. Profondi conoscitori dell’animo umano, in grado di prevedere le reazioni delle masse di fronte ad ogni tipo di evento, potrebbero progettare modelli catastrofici e predeterminare con una precisione disarmante la risposta delle persone comuni. Ad esempio di fronte alla probabilità che quattro aerei impazziscano nei cieli americani di una splendida mattina di settembre, oppure guardando i corpi smembrati di un attentato compiuto da una qualunque “sigla” islamica. Infine, potrebbero decidere come e quando dare una sferzata finale allo stress test, ad esempio con il pangolino. O era il pipistrello? È la *«forma legale di ciò che non può avere forma legale»*, più in generale lo spirito disumano dei governanti di oggi, la consuetudine della guerra preventiva, la quale impone con forza che *«lo stato di eccezione tende sempre più a presentarsi come il paradigma di governo dominante della politica contemporanea»*. Così analizza magistralmente Giorgio Agamben nel II° volume della raccolta Homo Sacer, intitolato per l’appunto [Stato di Eccezione](https://www.amazon.it/s?k=stato+di+eccezione+agamben&adgrpid=1234751876426057&hvadid=77172156923137&hvbmt=be&hvdev=c&hvlocphy=1861&hvnetw=s&hvqmt=e&hvtargid=kwd-77172234261086%3Aloc-93&hydadcr=18605_1867270&mcid=df58fe78258f374b81f1fd0eeaa1c659&msclkid=ea580711f461117b4cc160bdad34d584&tag=amamitsp-21&ref=pd_sl_7ni9dvsw1h_e). ## Stato indegno  Gli esseri umani, fondamentalmente miti e pacifici, tendono a condurre vite “normali” in ogni condizione ambientale. Un’unica variabile tende ad interferire per cambiare la condizione ambientale: la politica dello stato. E **lo fa in maniera sempre negativa**. Lo stato crea emergenze, per poi sbattere il suo (piccolissimo) pene sul tavolo e imporre con forza la soluzione, che tenderà puntualmente a facilitare la propria vita rendendo impossibile quella dei ~~cittadini~~ sudditi. Le disuguaglianze create hanno poi **il solo scopo di mettere** esseri miti e pacifici (ma sotto costante pressione) **gli uni contro gli altri**. Pensateci: da quanti decenni siete sotto la pressione di una *«forma legale di ciò che non può avere forma legale»*? Sentendo il Marchese del Grillo ***«Io so’ io, voi siete un cazzo»***, probabilmente è qualche secolo che questo stato indegno esiste. ## Vera natura o Nuda vita?  Il fatto, poi, che lo stato indegno venga accettato senza fiatare, fa parte di quella serie di reazioni delle masse e che i profondi conoscitori dell’animo umano sfruttano per mantenere il potere. Si passa poi alle peggiori angherie che lo stato indegno e i suoi agenti perpetrano nei confronti dei ~~cittadini~~ sudditi, alle estreme disparità tra ~~cittadini~~ sudditi e i “servitori” dello stato, chiamati così perché servono lo stato indegno e non i ~~cittadini~~ sudditi. Prima di arrivare alla sferzata finale dello stress test, persone miti e pacifiche hanno subito così tanti torti da non saperli più contare, ormai fanno parte della normalità. La loro esistenza è ormai ridotta a quello che Walter Benjamin prima e Giorgio Agamben poi definiscono la **Nuda Vita**, mettendo in analogia i sudditi con i detenuti di Guantanamo, giuridicamente innominabili e inclassificabili, ovvero ***«oggetto di una pura signoria di fatto»***. ## Il sontuoso master  Nello stato di eccezione in cui viviamo da almeno 50 anni, a parte pochi dotati di un immenso spirito di osservazione (e i profondi conoscitori al potere, chiaro), nessuno di noi ha mai avuto **veramente** il piacere di conoscere la reale natura delle persone con cui abbiamo scelto di circondarci. Magari c’era quel “piccolo tarlo”, quella “vocina” che ci ha fatto preferire alcuni piuttosto che altri, ma alla fine ha sempre prevalso l’attitudine mite e pacifica, che ha messo a tacere quella vocina. covid-1984 ha il merito di aver messo a nudo tutti: vittime e carnefici. Si tratta verosimilmente di **un sontuoso master che svelerà la vera natura di ognuno**, **nessuno escluso**. Ahinoi, il master è decennale e siamo appena all'inizio del V° anno accademico. ## Istruzioni, prima ancora che l’istruzione  Se c’è un consiglio che mi sento di dare a chi è ancora molto giovane, è proprio quello di non mettere mai a tacere quella “vocina”, per nessun motivo, seppure plausibile. Anche senza rovinare i rapporti, ma l’animo umano va sempre indagato, **si deve fare chiarezza sulla vera natura delle persone con cui si decide di fare un percorso di vita**. La scoperta porterà ad evitare tutti quei “servitori” dello stato di cose indegno di essere definito umano. I *compliant*, gli asserviti, quelli senza spina dorsale o, peggio, **che hanno un interesse personale a mantenere lo status quo** devono essere evitati a tutti i costi. È oltremodo doloroso, ma va fatto. Questi indegni devono essere isolati al più presto, in maniera da renderli innocui. Sono loro il vero esercito dello stato indegno, disposti a combattere qualunque guerra pur di rimediare un piccolissimo quanto ridicolo privilegio. Oggi, i tempi in cui questo esercito si abbassava a tanto per il classico piatto di lenticchie riscaldate, sono un lontanissimo ricordo. covid-1984 ha ulteriormente abbattuto lo standard: ora gli indegni fiancheggiano qualsiasi assurdità **in cambio di un piatto di lenticchie rimasticate dalla signoria di fatto**. L’unico risultato possibile è che l'infame stato rafforza il suo potere di controllo e rosicherà uno alla volta i (pochi) diritti e la libertà di chiunque. Ecco perché bisogna spuntare le armi di questo spregevole stato di cose colpendo l’anello debole, isolandolo. Debole perché non ci crede (nello stato) ma agisce asservito solo per quel piatto di lenticchie (quelle rimasticate e sputate). La prima volta che si incontrano, la vocina vi metterà di fronte alla sensazione di essere ai limiti di uno scontro frontale: capire da che parte andrà il rivale, per buttarsi in quella opposta ed evitare così uno schianto fatale. Fatelo: buttatevi dall’altra parte. E scegliete la parte giusta. @ a4a6b584:1e05b95b
2025-01-02 18:13:31## The Four-Layer Framework ### Layer 1: Zoom Out  Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what." **Example**: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems. - **Tip**: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage. _Once you have the big picture in mind, it’s time to start breaking it down._ --- ### Layer 2: Categorize and Connect  Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas. **Example**: Studying biology? Group concepts into categories like cells, genetics, and ecosystems. - **Tip**: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track. _With your categories in place, you’re ready to dive into the details that bring them to life._ --- ### Layer 3: Master the Details  Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable. **Example**: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language. - **Tip**: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding. _Now that you’ve mastered the essentials, you can expand your knowledge to include extra material._ --- ### Layer 4: Expand Your Horizons  Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams. **Example**: Learn about rare programming quirks or historical trivia about a language’s development. - **Tip**: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time. --- ## Pro Tips for Better Learning ### 1. Use Active Recall and Spaced Repetition Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information. ### 2. Map It Out Create visual aids like [diagrams or concept maps](https://excalidraw.com/) to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2. ### 3. Teach What You Learn Explain the subject to someone else as if they’re hearing it for the first time. Teaching **exposes any gaps** in your understanding and **helps reinforce** the material. ### 4. Engage with LLMs and Discuss Concepts Take advantage of tools like ChatGPT or similar large language models to **explore your topic** in greater depth. Use these tools to: - Ask specific questions to clarify confusing points. - Engage in discussions to simulate real-world applications of the subject. - Generate examples or analogies that deepen your understanding. **Tip**: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective. --- ## Get Started Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
@ a4a6b584:1e05b95b
2025-01-02 18:13:31## The Four-Layer Framework ### Layer 1: Zoom Out  Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what." **Example**: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems. - **Tip**: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage. _Once you have the big picture in mind, it’s time to start breaking it down._ --- ### Layer 2: Categorize and Connect  Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas. **Example**: Studying biology? Group concepts into categories like cells, genetics, and ecosystems. - **Tip**: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track. _With your categories in place, you’re ready to dive into the details that bring them to life._ --- ### Layer 3: Master the Details  Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable. **Example**: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language. - **Tip**: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding. _Now that you’ve mastered the essentials, you can expand your knowledge to include extra material._ --- ### Layer 4: Expand Your Horizons  Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams. **Example**: Learn about rare programming quirks or historical trivia about a language’s development. - **Tip**: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time. --- ## Pro Tips for Better Learning ### 1. Use Active Recall and Spaced Repetition Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information. ### 2. Map It Out Create visual aids like [diagrams or concept maps](https://excalidraw.com/) to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2. ### 3. Teach What You Learn Explain the subject to someone else as if they’re hearing it for the first time. Teaching **exposes any gaps** in your understanding and **helps reinforce** the material. ### 4. Engage with LLMs and Discuss Concepts Take advantage of tools like ChatGPT or similar large language models to **explore your topic** in greater depth. Use these tools to: - Ask specific questions to clarify confusing points. - Engage in discussions to simulate real-world applications of the subject. - Generate examples or analogies that deepen your understanding. **Tip**: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective. --- ## Get Started Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence. @ 575a8227:065bba95
2025-02-12 10:57:10https://www.youtube.com/watch?v=SiV7UhoiZM8 Hola nostr, El reciente podcast de lunaticoin con Salinas ha puesto sobre la mesa una reflexión profunda sobre el llamado "fondo estratégico Bitcoin" de Trump, revelando una paradoja que merece nuestra atención. Pensemos en el camino que hemos recorrido como individuos en el ecosistema Bitcoin. Durante años, cada uno de nosotros ha trabajado incansablemente, ahorrando con determinación para adquirir Bitcoin con dinero real, fruto de nuestro esfuerzo diario. En ese trayecto, hemos enfrentado críticas constantes: que si Bitcoin solo servía para actividades ilícitas, que si era un esquema Ponzi, que si carecía de valor intrínseco. Ahora, en 2025, presenciamos un giro narrativo sorprendente. Los mismos que demonizaron Bitcoin proponen crear un "fondo estratégico", ¿y cómo planean financiarlo? Con la misma herramienta contra la que Bitcoin nació para protegernos: la impresión infinita de dinero fiat. Pretenden adquirir con papel sin respaldo lo que a tantos nos ha costado años de esfuerzo y convicción conseguir. La comunidad Bitcoin se ha construido desde abajo, con personas que creyeron en el proyecto cuando pocos lo hacían, que mantuvieron sus convicciones en los momentos más difíciles, que construyeron infraestructura y educaron a otros. Somos nosotros, no los oportunistas de última hora, quienes hemos llevado Bitcoin hasta donde está hoy. La propuesta actual representa una doble expropiación: primero devalúan nuestros ahorros mediante la inflación, y luego utilizan ese mismo dinero devaluado para intentar acaparar Bitcoin. Es un mecanismo que perpetúa exactamente aquello contra lo que Bitcoin fue creado para luchar. Bitcoin nació como una herramienta de libertad financiera para el individuo, no como un instrumento más de control centralizado. Cada día que pasa, se hace más evidente que ningún político, independientemente de su retórica, representa los valores fundamentales de Bitcoin. En estos momentos, mantener nuestros sats no es solo una decisión financiera, es una declaración de principios. HODL 🟠₿
@ 575a8227:065bba95
2025-02-12 10:57:10https://www.youtube.com/watch?v=SiV7UhoiZM8 Hola nostr, El reciente podcast de lunaticoin con Salinas ha puesto sobre la mesa una reflexión profunda sobre el llamado "fondo estratégico Bitcoin" de Trump, revelando una paradoja que merece nuestra atención. Pensemos en el camino que hemos recorrido como individuos en el ecosistema Bitcoin. Durante años, cada uno de nosotros ha trabajado incansablemente, ahorrando con determinación para adquirir Bitcoin con dinero real, fruto de nuestro esfuerzo diario. En ese trayecto, hemos enfrentado críticas constantes: que si Bitcoin solo servía para actividades ilícitas, que si era un esquema Ponzi, que si carecía de valor intrínseco. Ahora, en 2025, presenciamos un giro narrativo sorprendente. Los mismos que demonizaron Bitcoin proponen crear un "fondo estratégico", ¿y cómo planean financiarlo? Con la misma herramienta contra la que Bitcoin nació para protegernos: la impresión infinita de dinero fiat. Pretenden adquirir con papel sin respaldo lo que a tantos nos ha costado años de esfuerzo y convicción conseguir. La comunidad Bitcoin se ha construido desde abajo, con personas que creyeron en el proyecto cuando pocos lo hacían, que mantuvieron sus convicciones en los momentos más difíciles, que construyeron infraestructura y educaron a otros. Somos nosotros, no los oportunistas de última hora, quienes hemos llevado Bitcoin hasta donde está hoy. La propuesta actual representa una doble expropiación: primero devalúan nuestros ahorros mediante la inflación, y luego utilizan ese mismo dinero devaluado para intentar acaparar Bitcoin. Es un mecanismo que perpetúa exactamente aquello contra lo que Bitcoin fue creado para luchar. Bitcoin nació como una herramienta de libertad financiera para el individuo, no como un instrumento más de control centralizado. Cada día que pasa, se hace más evidente que ningún político, independientemente de su retórica, representa los valores fundamentales de Bitcoin. En estos momentos, mantener nuestros sats no es solo una decisión financiera, es una declaración de principios. HODL 🟠₿