-
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note
-
 @ 8fb140b4:f948000c
2023-07-22 09:39:48
@ 8fb140b4:f948000c
2023-07-22 09:39:48Intro
This short tutorial will help you set up your own Nostr Wallet Connect (NWC) on your own LND Node that is not using Umbrel. If you are a user of Umbrel, you should use their version of NWC.
Requirements
You need to have a working installation of LND with established channels and connectivity to the internet. NWC in itself is fairly light and will not consume a lot of resources. You will also want to ensure that you have a working installation of Docker, since we will use a docker image to run NWC.
- Working installation of LND (and all of its required components)
- Docker (with Docker compose)
Installation
For the purpose of this tutorial, we will assume that you have your lnd/bitcoind running under user bitcoin with home directory /home/bitcoin. We will also assume that you already have a running installation of Docker (or docker.io).
Prepare and verify
git version - we will need git to get the latest version of NWC. docker version - should execute successfully and show the currently installed version of Docker. docker compose version - same as before, but the version will be different. ss -tupln | grep 10009- should produce the following output: tcp LISTEN 0 4096 0.0.0.0:10009 0.0.0.0: tcp LISTEN 0 4096 [::]:10009 [::]:**
For things to work correctly, your Docker should be version 20.10.0 or later. If you have an older version, consider installing a new one using instructions here: https://docs.docker.com/engine/install/
Create folders & download NWC
In the home directory of your LND/bitcoind user, create a new folder, e.g., "nwc" mkdir /home/bitcoin/nwc. Change to that directory cd /home/bitcoin/nwc and clone the NWC repository: git clone https://github.com/getAlby/nostr-wallet-connect.git
Creating the Docker image
In this step, we will create a Docker image that you will use to run NWC.
- Change directory to
nostr-wallet-connect:cd nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - The last line of the output (after a few minutes) should look like
=> => naming to docker.io/library/nwc:latest nwc:latestis the name of the Docker image with a tag which you should note for use later.
Creating docker-compose.yml and necessary data directories
- Let's create a directory that will hold your non-volatile data (DB):
mkdir data - In
docker-compose.ymlfile, there are fields that you want to replace (<> comments) and port “4321” that you want to make sure is open (check withss -tupln | grep 4321which should return nothing). - Create
docker-compose.ymlfile with the following content, and make sure to update fields that have <> comment:
version: "3.8" services: nwc: image: nwc:latest volumes: - ./data:/data - ~/.lnd:/lnd:ro ports: - "4321:8080" extra_hosts: - "localhost:host-gateway" environment: NOSTR_PRIVKEY: <use "openssl rand -hex 32" to generate a fresh key and place it inside ""> LN_BACKEND_TYPE: "LND" LND_ADDRESS: localhost:10009 LND_CERT_FILE: "/lnd/tls.cert" LND_MACAROON_FILE: "/lnd/data/chain/bitcoin/mainnet/admin.macaroon" DATABASE_URI: "/data/nostr-wallet-connect.db" COOKIE_SECRET: <use "openssl rand -hex 32" to generate fresh secret and place it inside ""> PORT: 8080 restart: always stop_grace_period: 1mStarting and testing
Now that you have everything ready, it is time to start the container and test.
- While you are in the
nwcdirectory (important), execute the following command and check the log output,docker compose up - You should see container logs while it is starting, and it should not exit if everything went well.
- At this point, you should be able to go to
http://<ip of the host where nwc is running>:4321and get to the interface of NWC - To stop the test run of NWC, simply press
Ctrl-C, and it will shut the container down. - To start NWC permanently, you should execute
docker compose up -d, “-d” tells Docker to detach from the session. - To check currently running NWC logs, execute
docker compose logsto run it in tail mode add-fto the end. - To stop the container, execute
docker compose down
That's all, just follow the instructions in the web interface to get started.
Updating
As with any software, you should expect fixes and updates that you would need to perform periodically. You could automate this, but it falls outside of the scope of this tutorial. Since we already have all of the necessary configuration in place, the update execution is fairly simple.
- Change directory to the clone of the git repository,
cd /home/bitcoin/nwc/nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - Change directory back one level
cd .. - Restart (stop and start) the docker compose config
docker compose down && docker compose up -d - Done! Optionally you may want to check the logs:
docker compose logs
-
 @ a60e79e0:1e0e6813
2025-03-28 08:47:35
@ a60e79e0:1e0e6813
2025-03-28 08:47:35This is a long form note of a post that lives on my Nostr educational website Hello Nostr.
When most people stumble across Nostr, they see is as a 'decentralized social media alternative' — something akin to Twitter (X), but free from corporate control. But the full name, "Notes and Other Stuff Transmitted by Relays", gives a clue that there’s more to it than just posting short messages. The 'notes' part is easy to grasp because it forms almost everyone's first touch point with the protocol. But the 'other stuff'? That’s where Nostr really gets exciting. The 'other stuff' is all the creative and experimental things people are building on Nostr, beyond simple text based notes.
Every action on Nostr is an event, a like, a post, a profile update, or even a payment. The 'Kind' is what specifies the purpose of each event. Kinds are the building blocks of how information is categorized and processed on the network, and the most popular become part of higher lever specification guidelines known as Nostr Implementation Possibility - NIP. A NIP is a document that defines how something in Nostr should work, including the rules, standards, or features. NIPs define the type of 'other stuff' that be published and displayed by different styles of client to meet different purposes.
Nostr isn’t locked into a single purpose. It’s a foundation for whatever 'other stuff' you can dream up.
Types of Other Stuff
The 'other stuff' name is intentionally vague. Why? Because the possibilities of what can fall under this category are quite literally limitless. In the short time since Nostr's inception, the number of sub-categories that have been built on top of the Nostr's open protocol is mind bending. Here are a few examples:
- Long-Form Content: Think blog posts or articles. NIP-23.
- Private Messaging: Encrypted chats between users. NIP-04.
- Communities: Group chats or forums like Reddit. NIP-72
- Marketplaces: People listing stuff for sale, payable with zaps. NIP-15
- Zaps: Value transfer over the Lightning Network. NIP57

Popular 'Other Stuff' Clients
Here's a short list of some of the most recent and popular apps and clients that branch outside of the traditional micro-blogging use case and leverage the openness, and interoperability that Nostr can provide.
Blogging (Long Form Content)
- Habla - Web app for Nostr based blogs
- Highlighter - Web app that enables users to highlight, store and share content
Group Chats
- Chachi Chat - Relay-based (NIP-29) group chat client
- 0xchat - Mobile based secure chat
- Flotilla - Web based chat app built for self-hosted communities
- Nostr Nests - Web app for audio chats
- White Noise - Mobile based secure chat
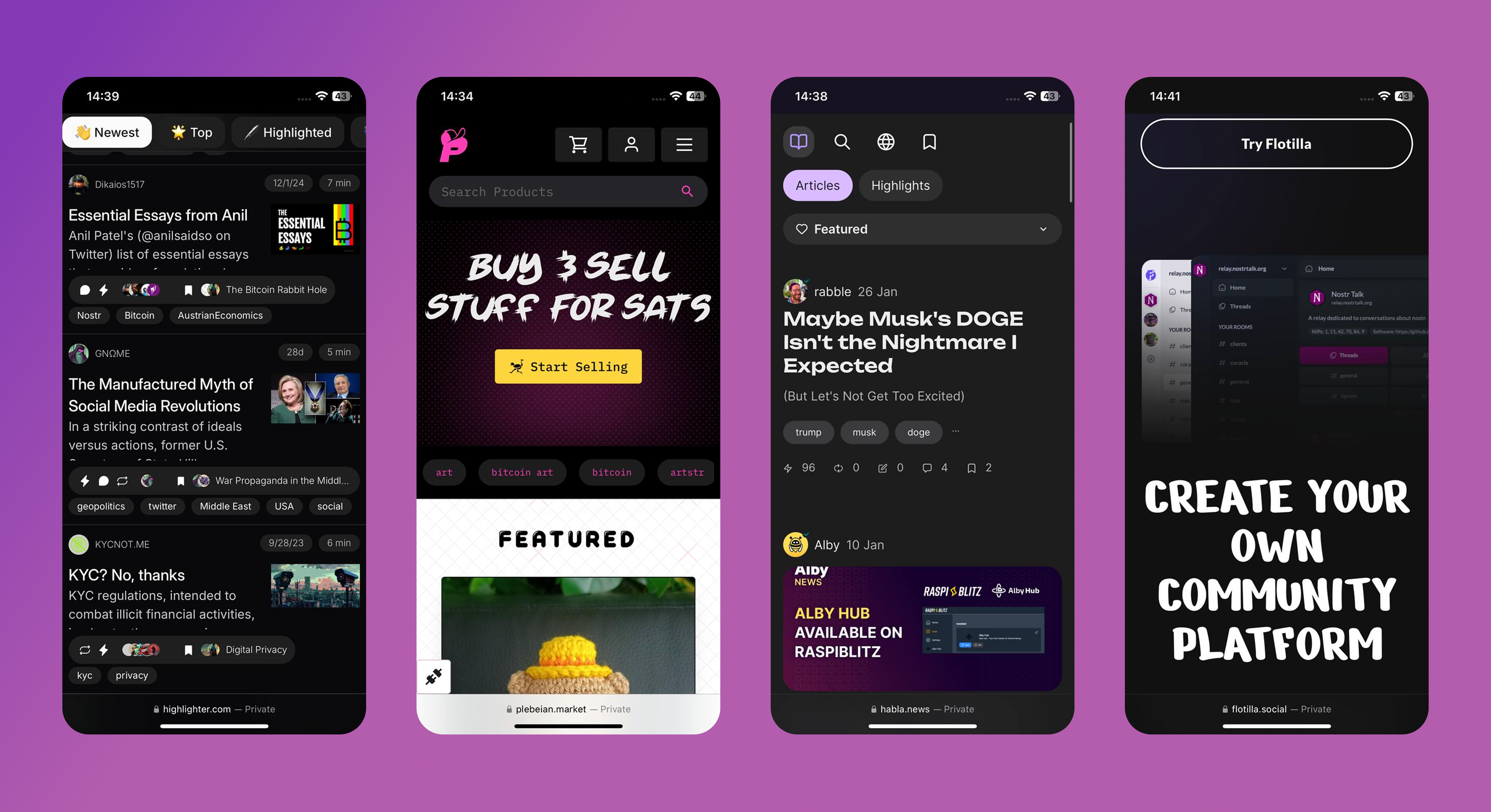
Marketplaces
- Shopstr - Permissionless marketplace for web
- Plebeian Market - Permissionless marketplace for web
- LNBits Market - Permissionless marketplace for your node
- Mostro - Nostr based Bitcoin P2P Marketplace
Photo/Video
Music
- Fountain - Podcast app with Nostr features
- Wavlake - A music app supporting the value-for-value ecosystem
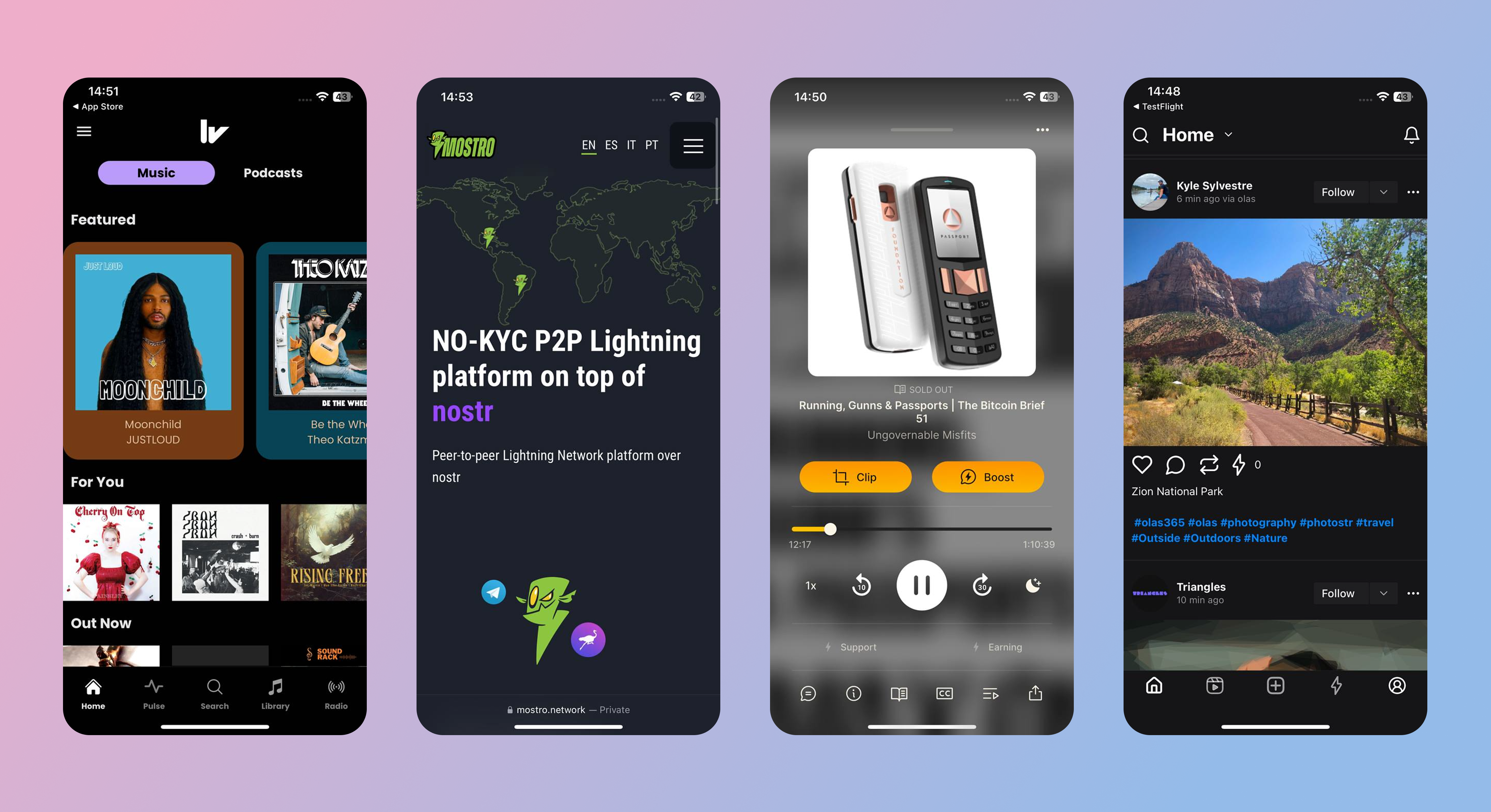
Livestreaming
- Zap.stream - Nostr native live streams
Misc
- Wikifreedia - Nostr based Wikipedia alternative
- Wikistr - Nostr based Wikipedia alternative
- Pollerama - Nostr based polls
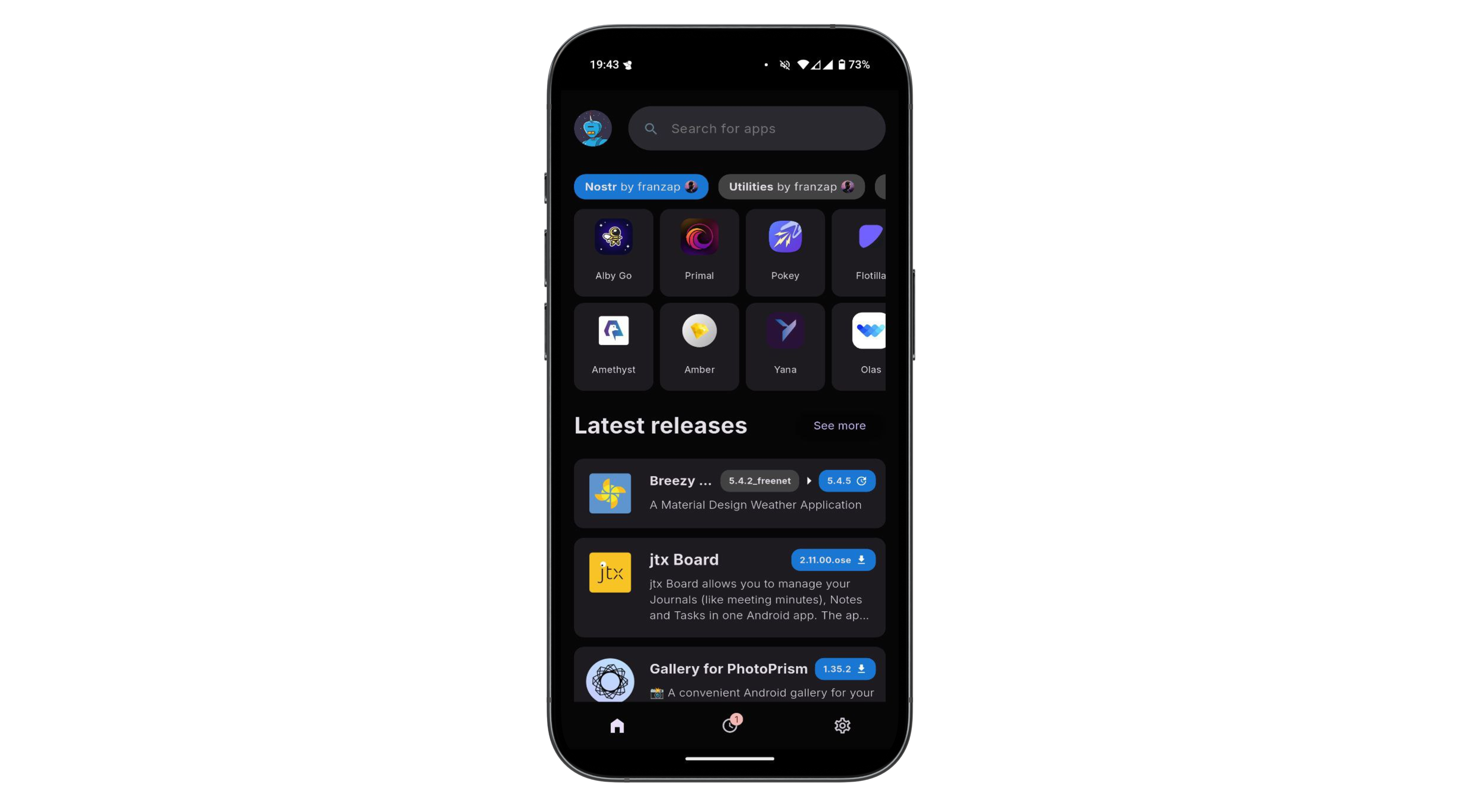
- Zap Store - The app store powered by your social graph
The 'other stuff' in Nostr is what makes it special. It’s not just about replacing Twitter or Facebook, it’s about building a decentralized ecosystem where anything from private chats to marketplaces can thrive. The beauty of Nostr is that it’s a flexible foundation. Developers can dream up new ideas and build them into clients, and the relays just keep humming along, passing the data around. It’s still early days, so expect the 'other stuff' to grow wilder and weirder over time!
You can explore the evergrowing 'other stuff' ecosystem at NostrApps.com, Nostr.net and Awesome Nostr.
-
 @ 2183e947:f497b975
2025-03-29 02:41:34
@ 2183e947:f497b975
2025-03-29 02:41:34Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison.
I can't tell you how to create your own accounts because it was made very clear that only some of the software is currently open source, and how this will all work is still a bit up in the air. The code that is open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core
You can also learn more about Pubky here: https://pubky.org/
That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key.
Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis.
Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed.
Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message.
I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key.
As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster.
Based on all of this info, it seems like, to populate your feed, this is the series of steps:
- you tell your homeserver your pubkey
- it uses some sort of algorithm to decide whose posts to show you
- then looks up the homeservers used by those people on an indexer server
- then it fetches posts from their homeservers
- then your client displays them to you
To create a post, this is the series of steps:
- you tell your homeserver what you want to say to the world
- it stores that message in plaintext and merely asserts that it came from you (it's not signed)
- other people can find out what you said by querying for your posts on your homeserver
Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver.
John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted.
Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/
-
 @ df06d21e:2b23058f
2025-03-29 02:08:31
@ df06d21e:2b23058f
2025-03-29 02:08:31Imagine a Living Civilization—a new way to see our world. It starts with the Universe’s pillars: Matter, the stuff we’re made of; Energy, the flow that drives us; Physics, the rules we play by; and Chemistry, the complexity that builds us. We know these well. But civilization? That’s our creation—and although it has been described in so many different ways over the years I thought it was time for something new. Civilization has its own pillars, systems that I call the pillars of the Metaverse: Capital, Information, Innovation, and Trust.
Capital is how we measure value. Not just money, but everything that matters: skills, we call that Human Capital; ecosystems, that’s Natural Capital; infrastructure, Public Capital; relationships, Social Capital. Picture a farmer swapping Bitcoin sats for seeds—not fiat debt—or tracking soil health alongside his wallet. Capital is a system, a system of measurement.
Information is how we verify truth. Think IPFS, a network holding real data—climate stats, farming fixes—open to all, not locked up by some corporate gatekeeper. Information is a system of verification.
Innovation is about generating solutions. On GitHub, coders worldwide crank out tools—Nostr clients, solar apps—shared freely, not patented for profit. Innovation is our system of generation.
And Trust—it’s coordination. Nostr’s decentralized threads let communities set trade rules, split resources—governance from the ground up, no overlords required. Trust is our system of coordination.
Right now we’re stuck in debt-based systems—and they’re failing us. Take fiat currency—central banks print it, slashing your purchasing power. Our dollar buys less every year; savings erode while the elite stack their gains. It’s a scam, Bitcoiners know it—fiat’s the real Ponzi bleeding us dry. Capital gets twisted—firms hoard Bitcoin for fiat pumps, not real wealth; governments chase GDP while forests die and skills sit idle. Information is buried—our media spits out spin, our corporations lock truth in silos. Innovation is stalled—debt props up corporate patents, not open wins. Trust is gone—our governance systems consist of top-down control that splits us apart, left to right, top to bottom. Debt just measures scarcity—money borrowed, nature trashed, bonds frayed—and it’s crushing the pillars.
Wealth-based systems promise to turn that around. Bitcoin’s sound money is just the start—sats hold value, not inflate it away. Real capital measures what sustains us—sats fund a cooperative's water pump, not a vault; they track skills taught, land healed, ties rebuilt. Real Information opens up—IPFS logs show ‘biochar boosted yield 20%’, verified by us, not suits. Real Innovation flows—GitHub devs build Lightning hubs, wealth spreads. Real Trust binds us together—Nostr chats align us, no central puppeteer. Wealth based systems strengthen the pillars of the Metaverse, it doesn’t erode them.
We needed a new framing. A new vision of what was, what is, and what could be. We have one. This is real. This is the world we are building. Bitcoin is live, Nostr is growing, IPFS and GitHub are humming. We can see Debt teetering; while real wealth is rising. So, hodlers, maxis, plebs—everyone—what does a true wealth-based system look like? How can we measure Capital beyond fiat’s con job? Bitcoin’s the rock, but it’s just the beginning. How do we build on this, expand it, and transform everything as we build something entirely new?
-
 @ f1989a96:bcaaf2c1
2025-03-27 13:53:14
@ f1989a96:bcaaf2c1
2025-03-27 13:53:14Good morning, readers!
Turkey’s currency plunged to a record low after the arrest of Istanbul Mayor Ekrem Imamoglu, one of President Recep Tayyip Erdogan’s main political rivals. This follows a pattern of escalating repression of opposition figures, which have been described as an effort to suppress competition ahead of primary elections. As economic conditions deteriorate, Erdogan is resorting to desperate measures — blocking social media, arresting dissenters, and tear-gassing protests — to maintain power over an increasingly restless populace.
In the Caribbean, we shed light on Cubans' struggles accessing remittances sent from family members abroad. This is a symptom of the regime's strict monetary controls over foreign currency. Cubans face long delays or can’t withdraw cash due to bank liquidity shortages. And when they can, remittances are converted into pesos at the overvalued official Cuban exchange rate. This effectively allows the Communist Party of Cuba (PCC) to loot the value from Cuban remittances.
In freedom tech news, we highlight Demand Pool, the first-ever Stratum V2 mining pool. Stratum V2 is a mining protocol designed to decentralize Bitcoin mining by letting individual miners create their own block templates rather than relying on centralized pools to do so for them. This improves censorship resistance and promotes a more decentralized and resilient Bitcoin network — critical features for human rights defenders and nonprofits using Bitcoin to protect against financial repression from authoritarian regimes.
We end by featuring Vijay Selvam's new book, “Principles of Bitcoin.” It offers a clear, first-principles guide to understanding how Bitcoin’s technology interacts with economics, politics, philosophy, and human rights. Whether you’re new to Bitcoin or looking to deepen your understanding, this book provides a solid foundation, and it even features a foreword by HRF Chief Strategy Officer Alex Gladstein.
Now, let’s dive right in!
Subscribe Here
GLOBAL NEWS
Turkey | Lira in Free Fall as Erdogan Arrests Political Rival
Turkey’s lira plunged to a record low after officials arrested Istanbul Mayor Ekrem Imamoglu, President Recep Tayyip Erdogan’s main political rival. Imamoglu’s arrest comes ahead of primary elections and follows the increasing repression of opposition figures in recent months, including the suspension of political opposition accounts on X. Officials also arrested Buğra Gökçe, head of the Istanbul Planning Agency, for publishing data exposing the country’s deepening poverty. The currency’s fallout and political repression have sparked protests in Istanbul despite a four-day ban. The regime is responding with tear gas and rubber bullets. Meanwhile, Turks dissenting online risk joining over a dozen other citizens recently arrested for “provocative” social media posts. Netblocks reports that the Turkish regime imposed restrictions on social media and messaging to quell the uprising of Turks struggling with financial conditions and deepening repression.
Cuba | Banks “Hijack” Citizen Remittances
Cubans are struggling to access remittances sent from their families abroad. This is because the regime completely controls all incoming foreign currency transfers. When remittances arrive, communist banking authorities force their conversion into collapsing Cuban pesos or “Moneda Libremente Convertible” (MLC), Cuba’s digital currency with limited use. On top of this, Cubans receive pesos in their accounts based on the official Cuban exchange rate, which is far below the informal market rate. This allows the regime to opaquely siphon off much of the remittances’ real value. Even when the money clears, Cubans face long delays or can’t withdraw the cash due to banks’ liquidity shortages. Many Cubans are accusing these banks of “hijacking” their remittances. As inflation, electrical blackouts, and food shortages continue, remittances are more critical than ever for Cuban families. Yet, they’re blocked at every turn by a system designed to impoverish them.
Pakistan | Announces Plans to Regulate Digital Assets
Pakistan announced plans to create a regulatory framework for Bitcoin and digital assets to attract foreign investment and domestic economic activity. It’s a peculiar shift for a regime that regularly suspends the Internet, censors social media, represses opposition, and burdens its people with the highest cost of living in Asia. We suspect the plans indicate efforts to control the industry rather than empower individuals. The military-backed regime is also exploring a Central Bank Digital Currency (CBDC) and tightening controls on VPN use, which are hardly the hallmarks of leadership committed to permissionless financial systems. But perhaps it matters little. Grassroots Bitcoin adoption in Pakistan already ranks among the highest in the world, with an estimated 15 to 20 million users turning to digital assets to preserve their savings, circumvent financial controls, and escape the failures of a collapsing fiat system. HRF supported Bitcoin Pakistan with a grant to help translate resources into Urdu, a language spoken by 60 million people trapped in this repressive scenario.
Russia | Piloting CBDC in Tatarstan to Test Smart Contract Functionality
Russia’s central bank plans to pilot its CBDC, the digital ruble, in Tatarstan to test smart contract functionality. Specifically, the central bank will experiment with conditional spending, using smart contracts to restrict where and what users can spend money on. If these features are implemented, it will empower the Kremlin with micro-controls over Russians’ spending activity. Officials could program funds to expire, restrict purchases to regime-approved goods, or block transactions at certain locations — leaving users with no financial autonomy or privacy. Those who oppose the Russian dictatorship, such as activists, nonprofits, and dissenters, could be debanked with more ease, their assets frozen or confiscated without recourse.
Nicaragua | Government Mandates Public Employees Declare All Assets
In Nicaragua, dictator Daniel Ortega intensified state financial surveillance by mandating all public servants to disclose information on all personal and family assets. The mandate requires all public employees to declare everything from personal bank accounts, loans, vehicles, and other assets — as well as the assets and accounts of immediate family members. Those who do not comply face the threat of termination. Ironically, despite the law requiring such disclosure, Ortega himself has not declared his assets since 2006. Under the guise of regulatory compliance, this policy is yet another link in the chain tightening state surveillance over Nicaraguan society. Bitcoin adoption continues to grow in this repressed Central American nation.
BITCOIN AND FREEDOM TECH NEWS
Demand Pool | First Stratum V2 Mining Pool Launches
Bitcoin mining could become more decentralized and censorship-resistant with the launch of Demand Pool, the first mining pool to ever implement Stratum V2. Stratum V2 is open-source software that allows miners to build their own block templates, enabling more individual mining and less dependence on large and centralized mining pools. This helps maintain Bitcoin’s key features: its decentralized, permissionless, and uncensorable nature. All of which are crucial for human rights defenders and nonprofits bypassing the financial repression and surveillance of authoritarian regimes. Learn more here.
Bitcoin Mining | Three Solo Blocks Found
Three separate solo miners mined Bitcoin blocks in the past seven days. This marks the second, third, and fourth solo blocks mined in the past two weeks alone, hinting at a surge in home mining. This promotes greater decentralization within the Bitcoin network because solo miners have little functional ability to censor. In contrast, large mining pools are points of failure that centralized interests can more easily pressure — to the detriment of activists and human rights defenders. The first block was mined on March 21 by a miner using a self-hosted FutureBit Apollo machine that earned 3.125 BTC plus fees for processing block 888,737. Just days later, a solo miner with under 1 TH/s of self-hosted hash rate found block 888,989, which became just the third block ever to be mined using an open-source Bitaxe device. Most recently, on March 24, a solo miner using a $300 setup successfully mined block 889,240.
Krux | Adds Taproot and Miniscript Support
Krux, open-source software for building your own Bitcoin signing devices (hardware for Bitcoin self-custody), released an update that enhances privacy and flexibility. The update introduces support for Taproot, a past Bitcoin upgrade that improves privacy and security, and Miniscript, a simplified way to create more complex Bitcoin transaction rules. This allows users to manage multi-signature wallets (where more than one private key is required to interact with your Bitcoin) in a more private and flexible way. It also enables spending conditions that are harder to censor and easier to verify. Krux continues to support the struggle for financial freedom and human rights by breaking down barriers to Bitcoin self-custody. HRF has recognized this impact and awarded grants to open-source developers working on Krux to advance this mission.
Cashu | Developing Tap-to-Pay Ecash
Calle, the creator of Cashu, an open-source Chaumian ecash protocol for Bitcoin integrated with the Lightning Network, is developing a new tap-to-pay feature that enables instant, offline ecash payments via NFC. Ecash functions as a bearer asset, meaning the funds are stored directly on the user’s device. With tap-to-pay, it can be transferred with a single tap (similar to tapping your credit card). More generally, ecash offers fast, private transactions resistant to surveillance and censorship. But for activists and dissenters, this particular advancement makes private and permissionless payments more accessible and user-friendly. This development will be worth following closely. Watch a demo here.
OpenSats | Announces 10th Wave of Bitcoin Grants
OpenSats, a public nonprofit that supports open-source software and projects, announced its 10th wave of grants supporting Bitcoin initiatives. This round includes funding for Stable Channels, which enable stabilized Bitcoin-backed balances on the Lightning Network (allowing users to peg Bitcoin to fiat currencies in a self-custodial way) that provide stable, censorship-resistant payments. OpenSats also renewed its support for Floresta, a lightweight Bitcoin node (a computer that runs the Bitcoin software). It lowers entry barriers to running Bitcoin, helping make the network more decentralized and censorship-resistant.
Bitcoin Policy Institute | Launches Bitcoin Summer Research Program
The Bitcoin Student Network (BSN) and the Bitcoin Policy Institute (BPI) are teaming up to offer students an eight-week research internship this summer. The program is part of BPI’s Research Experiences for Undergraduates (REU) initiative and invites students passionate about the future of money, financial inclusion, and Bitcoin’s civil liberties impacts to conduct hands-on research. Participants will also receive mentorship from BPI researchers. The program runs from June 9 to Aug. 8, 2025, and includes an in-person colloquium in Washington, DC. It is an incredible opportunity for students worldwide, especially those living in oppressive regimes, to get involved with Bitcoin. Applications are open until April 7. Apply here.
RECOMMENDED CONTENT
Principles of Bitcoin by Vijay Selvam
“Principles of Bitcoin” by Vijay Selvam is a new book offering a first-principles guide to understanding Bitcoin’s technology, economics, politics, and philosophy. With a foreword by HRF Chief Strategy Officer Alex Gladstein, the book cuts through the noise to explain why Bitcoin stands alone as a tool for individual empowerment and financial freedom. Selvam’s work makes the case for Bitcoin as a once-in-history invention shaping a more decentralized and equitable future. Read it here.
Rule Breakers — The True Story of Roya Mahboob
“Rule Breakers” is a new film that tells the true story of Roya Mahboob, Afghanistan’s first female tech CEO, who empowered young girls in Afghanistan with financial literacy, robotics, and financial freedom through Bitcoin. The film recounts Mahboob’s courageous work educating these girls despite huge personal risks under a regime that bans their education. It follows the story of Afghan Dreamers, the country’s first all-girls robotics team, and the obstacles they overcome to compete on the world stage. “Rule Breakers” is a testament to the power of education, innovation, and resilience in the face of oppression. It’s now in theaters, and you can watch the trailer here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 6b3780ef:221416c8
2025-03-26 18:42:00
@ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments.
Understanding MCP Systems
MCP (Model Context Protocol) systems consist of two main components that work together:
- MCP Server: The heart of the system that exposes tools, which you can access via the
.listTools()method. - MCP Client: The interface that connects to the MCP server and lets you use the tools it offers.
These servers and clients can communicate using different transport methods:
- Standard I/O (stdio): A simple local connection method when your server and client are on the same machine.
- Server-Sent Events (SSE): Uses HTTP to create a communication channel.
For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr.
Creating (or Finding) an MCP Server
Building an MCP server is simpler than you might think:
- Create software in any programming language you're comfortable with.
- Add an MCP library to expose your server's MCP interface.
- Create an API that wraps around your software's functionality.
Once your server is ready, an MCP client can connect, for example, with
bun index.js, and then call.listTools()to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy.Alternatively, you can use one of the many existing MCP servers available in various repositories.
For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/
Setting Up the Workshop
Let's get hands-on:
First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script:
curl -fsSL https://bun.sh/install | bash-
Choose your MCP server: You can either create one or use an existing one.
-
Inspect your server using the MCP inspector tool:
bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2This will: - Launch a client UI (default: http://localhost:5173)
- Start an MCP proxy server (default: port 3000)
-
Pass any additional arguments directly to your server
-
Use the inspector: Open the client UI in your browser to connect with your server, list available tools, and test its functionality.
Deploying with DVMCP
Now for the exciting part – making your MCP server available to everyone on Nostr:
-
Navigate to your MCP server directory.
-
Run without installing (quickest way):
npx @dvmcp/bridge -
Or install globally for regular use:
npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridgeThen run using:bash dvmcp-bridge
This will guide you through creating the necessary configuration.
Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing.
For the configuration, you can set the relay as
wss://relay.dvmcp.fun, or use any other of your preferenceTesting and Integration
- Visit dvmcp.fun to see your DVM announcement.
- Call your tools and watch the responses come back.
For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime.
Integrating with LLM Clients
You can also integrate your DVMCP deployment with LLM clients using the discovery package:
-
Install and use the
@dvmcp/discoverypackage:bash npx @dvmcp/discovery -
This package acts as an MCP server for your LLM system by:
- Connecting to configured Nostr relays
- Discovering tools from DVMCP servers
-
Making them available to your LLM applications
-
Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1...
# Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ```
Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at dvmcp.fun.
This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications.
Final thoughts
If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun.
You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless.
However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr.
Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag.
Useful Resources
- Official Documentation:
- Model Context Protocol: modelcontextprotocol.org
-
DVMCP.fun: dvmcp.fun
-
Source Code and Development:
- DVMCP: github.com/gzuuus/dvmcp
-
DVMCP.fun: github.com/gzuuus/dvmcpfun
-
MCP Servers and Clients:
- Smithery AI: smithery.ai
- MCP.so: mcp.so
-
Glama AI MCP Servers: glama.ai/mcp/servers
Happy building!
- MCP Server: The heart of the system that exposes tools, which you can access via the
-
 @ 3e6e0735:9e95c8a2
2025-03-28 23:58:02
@ 3e6e0735:9e95c8a2
2025-03-28 23:58:02https://i.nostr.build/lanoHI3p2aCKRZlV.png
I’ve been thinking a lot lately about why Bitcoin still feels so misunderstood. Not just by the media or the IMF — that part’s predictable. But even inside our own circles, something's missing.
We say it’s money. We say it’s freedom. We say it’s code. And it is. But when you really zoom out, past the price and the politics, it’s something more radical than we usually admit.
Bitcoin is a shift in how power moves. And what we do with that power now actually matters.
The noise outside
Let’s start with the obvious: the media still doesn’t get it. Every other headline is either a death knell or a celebration depending on the price that day. No context. No nuance. No understanding of what we’re building.
You’ve seen the headlines: - “Bitcoin is crashing again.” - “Crypto bros are killing the planet.” - “The IMF warns: Bitcoin adoption is dangerous.”
Yeah? Dangerous to what?
The system they control. The levers they pull. The old game where the house always wins.
That’s why they’re afraid. Not because Bitcoin is volatile, but because it doesn’t ask permission.
This isn’t about panic — it’s about patterns
I’m not saying there’s a conspiracy. But there is inertia. Institutions protect themselves. Systems reinforce themselves. They were never going to roll out the red carpet for an open, borderless network that replaces their function.
So the IMF calls it a threat. Central banks scramble to launch CBDCs. And journalists keep writing the same shallow takes while ignoring the real story.
Meanwhile, we’re still here. Still building. Still holding. Still running nodes.
Bitcoin isn’t perfect. But it’s honest. It doesn’t bend to popularity or political pressure. It enforces rules with math, not people. And that’s exactly why it works.
Even we miss it sometimes
Here’s the part that really hit me recently: even within Bitcoin, we often undersell what this is.
We talk about savings. Inflation. Fiat debasement. All real, all important.
But what about the broader layer? What about governance? Energy? Communication? Defense?
Jason Lowery’s book Softwar lit that fuse for me again. Not because it’s flawless — it’s not. But because he reframed the game.
Bitcoin isn’t a new weapon. It’s the end of weapons-as-power.
Proof-of-work, in Lowery’s view, is a form of peaceful negotiation. A deterrent against coercion. A way to shift from kinetic violence to computational resolution.
Most people — even many Bitcoiners — haven’t fully absorbed that.
It’s not about militarizing the network. It’s about demilitarizing the world through energy expenditure that replaces human conflict.
Let’s be clear: this doesn’t mean Bitcoin will be used this way. It means it can. And that opens up a few possible futures:
- Scenario A: Smaller nations adopt Bitcoin infrastructure as a shield — a deterrent and neutral layer to build sovereignty
- Scenario B: Superpowers attack mining and self-custody, escalating regulatory capture and fragmenting the open protocol into corporate silos
- Scenario C: Bitcoin becomes the boring backend of legacy finance, its edge neutered by ETFs and custody-as-a-service
Which one wins depends on what we build — and who steps up.
Then I found Maya
I came across Maya Parbhoe’s campaign by accident. One of those late-night rabbit holes where Bitcoin Twitter turns into a global map.
She’s running for president of Suriname. She’s a Bitcoiner. And she’s not just tweeting about it — she’s building an entire political platform around it.
No central bank. Bitcoin as legal tender. Full fiscal transparency. Open-source government.
Yeah. You read that right. Not just open-source software — open-source statehood.
Her father was murdered after exposing corruption. That’s not a talking point. That’s real-life consequence. And instead of running away from systems, she’s choosing to redesign one.
That’s maximalism. Not in ideology. In action.
The El Salvador experiment — and evolution
When El Salvador made Bitcoin legal tender in 2021, it lit up our feeds. It was bold. Unprecedented. A true first.
But not without flaws.
The rollout was fast. Chivo wallet was centralized. Adoption stalled in rural areas. Transparency was thin. And despite the brave move, the state’s underlying structure remained top-down.
Bukele played offense, but the protocol was wrapped in traditional power.
Maya is doing it differently. Her approach is grassroots-forward. Open-source by design. Focused on education, transparency, and modular state-building — not just mandates.
She’s not using Bitcoin to prop up state power. She’s using it to distribute it.
Maximalism is evolving
Look, I get it. The memes are fun. The laser eyes. The beefsteak meetups. The HODL culture.
But there’s something else growing here. Something a little quieter, a little deeper: - People running nodes to protect civil liberties - Communities using Lightning for real commerce - Builders forging tools for self-sovereign identity - Leaders like Maya testing what Bitcoin can look like as public infrastructure
This is happening. In real time. It’s messy and fragile and still small. But it’s happening.
Let’s also stay honest:
Maximalism has its risks. Dogma can blind us. Toxicity can push people away. And if we’re not careful, we’ll replace one centralization with another — just wearing different memes.
We need less purity, more principles. Less hype, more clarity. That’s the kind of maximalism Maya embodies.
What now?
Maya doesn’t have a VC fund or an ad agency. She has a message, a mission, and the courage to put Bitcoin on the ballot.
If that resonates, help her. Not just by donating — though here’s the link:
https://geyser.fund/project/maya2025
But by sharing. Writing. Talking. Translating. Connecting.
Bitcoin is still early. But it’s not abstract anymore.
This isn’t just theory.
It’s a protocol, sure. But now, maybe it’s a presidency too.
https://i.nostr.build/0luYy8ojK7gkxsuL.png
-
 @ 7d33ba57:1b82db35
2025-03-28 22:14:24
@ 7d33ba57:1b82db35
2025-03-28 22:14:24Preko is a charming seaside town on Ugljan Island, just a short ferry ride from Zadar. Known for its beautiful beaches, relaxed atmosphere, and stunning views of the Adriatic, it's the perfect place to experience authentic Dalmatian island life.
🌊 Top Things to See & Do in Preko
1️⃣ Swim at Jaz Beach 🏖️
- A Blue Flag beach with clear turquoise waters and soft pebbles.
- Ideal for families thanks to its shallow waters.
- Nearby cafés and restaurants make it a great spot to spend the day.
2️⃣ Visit the Islet of Galevac 🏝️
- A tiny island just 80 meters from Preko, reachable by swimming or a short boat ride.
- Home to a 15th-century Franciscan monastery, surrounded by lush greenery.
- A peaceful retreat, perfect for relaxation.
3️⃣ Hike to St. Michael’s Fortress (Sv. Mihovil) 🏰
- A medieval fortress from the 13th century with breathtaking panoramic views.
- Overlooks Zadar, Kornati Islands, and the Adriatic Sea.
- A 1-hour scenic hike from Preko or accessible by bike or car.
4️⃣ Explore the Local Taverns & Seafood Restaurants 🍽️
- Try fresh seafood, octopus salad, and Dalmatian peka (slow-cooked meat & vegetables).
- Best spots: Konoba Roko (authentic seafood) & Vile Dalmacija (beachfront dining).
5️⃣ Rent a Bike or Scooter 🚲
- Explore Ugljan Island’s olive groves, hidden coves, and coastal paths.
- Visit nearby villages like Kali and Kukljica for more local charm.

6️⃣ Take a Day Trip to Zadar ⛵
- Just 25 minutes by ferry, Zadar offers historic landmarks, the Sea Organ, and Roman ruins.
- Perfect for a cultural excursion before returning to the peaceful island.
🚗 How to Get to Preko
🚢 By Ferry:
- From Zadar: Regular ferries (Jadrolinija) take ~25 minutes.
🚘 By Car:
- If driving, take the ferry from Zadar to Preko and explore the island.
🚴 By Bike:
- Many visitors rent bikes to explore Ugljan Island’s coastal roads.💡 Tips for Visiting Preko
✅ Best time to visit? May–September for warm weather & swimming 🌞
✅ Ferry schedules – Check times in advance, especially in the off-season ⏳
✅ Bring cash – Some smaller taverns and cafés may not accept cards 💰
✅ Stay for sunset – The views over Zadar from Preko’s waterfront are stunning 🌅Would you like hotel recommendations, hidden beaches, or other island activities? 😊
-
 @ fe9e99a0:5123e9a8
2025-03-28 21:25:43
@ fe9e99a0:5123e9a8
2025-03-28 21:25:43What’s happening?
-
 @ 7d33ba57:1b82db35
2025-03-28 20:59:51
@ 7d33ba57:1b82db35
2025-03-28 20:59:51Krka National Park, located in central Dalmatia, is one of Croatia’s most breathtaking natural wonders. Famous for its stunning waterfalls, crystal-clear lakes, and lush forests, the park is a must-visit for nature lovers. Unlike Plitvice Lakes, Krka allows swimming in certain areas, making it a perfect summer escape.
🌊 Top Things to See & Do in Krka National Park
1️⃣ Skradinski Buk Waterfall 💦
- The largest and most famous waterfall in the park, with cascading pools and wooden walkways.
- You used to be able to swim here, but since 2021, swimming is no longer allowed.
- Perfect for photography and picnics.
2️⃣ Roški Slap Waterfall 🌿
- A less crowded but equally beautiful series of waterfalls.
- Known for its "necklace" of small cascades leading into the main fall.
- Nearby Mlinica, a restored watermill, shows traditional Croatian life.
3️⃣ Visovac Island & Monastery 🏝️
- A tiny island in the middle of the Krka River, home to a Franciscan monastery from the 15th century.
- Accessible by boat tour from Skradinski Buk or Roški Slap.
- A peaceful, scenic spot with stunning views of the lake.
4️⃣ Krka Monastery 🏛️
- A Serbian Orthodox monastery hidden deep in the park.
- Built on ancient Roman catacombs, which you can explore.
- A quiet, spiritual place, often overlooked by tourists.
5️⃣ Hike & Walk the Nature Trails 🥾
- The park has several well-marked trails through forests, waterfalls, and lakes.
- Wooden walkways allow easy access to the main sights.
- Wildlife spotting: Look out for otters, turtles, and over 200 bird species!
6️⃣ Swim at Skradin Beach 🏖️
- While you can’t swim at Skradinski Buk anymore, Skradin Beach, just outside the park, is a great spot for a dip.
- Kayaking and boat tours available.
🚗 How to Get to Krka National Park
✈️ By Air: The nearest airport is Split (SPU), 1 hour away.
🚘 By Car:
- Split to Krka: ~1 hour (85 km)
- Zadar to Krka: ~1 hour (75 km)
- Dubrovnik to Krka: ~3.5 hours (280 km)
🚌 By Bus: Direct buses from Split, Zadar, and Šibenik to the park’s entrances.
🚢 By Boat: From Skradin, you can take a boat ride into the park.
💡 Tips for Visiting Krka National Park
✅ Best time to visit? Spring & early autumn (April–June, September–October) – Fewer crowds & mild weather 🍃
✅ Start early! Arrive before 10 AM to avoid crowds, especially in summer ☀️
✅ Bring water & snacks – Limited food options inside the park 🍎
✅ Wear comfy shoes – Wooden walkways & trails can be slippery 👟
✅ Take a boat tour – The best way to see Visovac Island & hidden spots ⛵
✅ Buy tickets online – Save time at the entrance 🎟️ -
 @ da0b9bc3:4e30a4a9
2025-03-28 19:14:52
@ da0b9bc3:4e30a4a9
2025-03-28 19:14:52It's Finally here Stackers!
It's Friday!
We're about to kick off our weekends with some feel good tracks.
Let's get the party started. Bring me those Feel Good tracks.
Let's get it!
https://youtu.be/r1ATFedwjnk?si=tPtLac6ExYZCx3Ez
originally posted at https://stacker.news/items/928119
-
 @ 3c389c8f:7a2eff7f
2025-03-28 17:10:17
@ 3c389c8f:7a2eff7f
2025-03-28 17:10:17There is a new web being built on Nostr. At it's core, is a social experience paralleled by no other decentralized protocol. Nostr not only solves the problems of siloed relationships, third-party identity ownership, and algorithmic content control; it makes possible a ubiquitous social network across almost anything imaginable. User controlled identity, open data, and verifiable social graphs allow us to redefine trust on the web. We can interact with each other and online content in ways that have previously only been pipedreams. Nostr is not just social media, it is the web made social.
Interoperability
The client/relay relationship on Nostr allows for almost endless data exchange between various apps, clients, relays, and users. If any two things are willing to speak the same sub-protocol(s) within Nostr, they can exchange data. Making a friend list enables that list to be used in any other place that chooses to make it available. Creating a relay to serve an algorithmic social feed makes that feed viewable in any client that displays social feeds. Health data held by a patient can be shared with any care provider, verified by their system, and vice versa. This is the point where I have to acknowledge my own tech-deaf limitations and direct you towards nostr.com for more information.
Data Resiliency
I prefer to use the term resiliency here, because its really a mix of data redundancy and self-managed data that creates broad availability. Relays may host 10, 20, 30+ copies of your notes in different locations, but you also have no assurance that those relays will hosts those notes forever. An individual operating their own relay, while also connecting to the wider network, ensures resiliency in events such that wide swaths of the network should disappear or collude against an individual. The simplicity of relay management makes it possible for nearly anyone to make sure that they have a way to convey their messages to their individual network, whether that be close contacts, an audience, or one individual. This resiliency doesn't just apply to typical speech, it applies to any data intended to be shared amongst humans and machines alike.
Pseudonymity and Anonymity
With privacy encroachment from corporations, advertisers, and governments reaching all time highs, the need for identity protecting tools is also on the rise. Nostr utilizes public key encryption for its identity system. As there is no central entity to "verify" you, there is no need to expose any personal identifiable information to any Nostr app, client, or relay. You can protect your personal identity by simply choosing not to expose it. Your reputation will build as you interact with others on the Nostr network. Your social capital can speak for itself. (As with everything else, utilizing a VPN is recommended.)
Identity and Provability
No one can stop an impersonator from trying to hijack an identity. With Nostr, you CAN prove that you are you, though, which is basically the same as saying "that person is not me" Every note you write, every action you take, is cryptographically signed by your private key. As long as you maintain control of that key, you can prove what you did or did not do.
Censorship Resistance
If you have read our Relay Rundown then you probably get the idea. If not here's the tl;dr: Many small, lightweight relays make up Nostr's distribution system. They are simple enough that anyone can run one. They are redundant enough that you can be almost certain your content exists somewhere. If that is not peace of mind enough, you can run your own with ease. Censorship resistance isn't counting on one company, man, or server to protect what you say. It is taking control of your speech. Nostr makes it easy.
Freedom of Mind and Association
Nostr eliminates the need for company run algorithms that high-jack your attention to feed the advertising industry. You are free to choose your social media experience. Nostr's DVMs, curations, and conversation-centered relays offer discovery mechanisms run by any number of providers. That could be an individual, a company, a group, or you. Many clients incorporate different ways of engaging with these corporate algorithm alternatives. You can also choose to keep a purely chronological feed of the the things and people you follow. Exploring Nostr through its many apps opens up a the freedom to choose what and how you feed your mind.
When we are able to explore, we end up surrounding ourselves with people who share our interests & hobbies. We find friends. This creates distance between ideologies and stark beliefs that often are used as the basis for the term "being in a bubble". Instead of bubbling off, an infinitely open space of thoughts and ideas allows for groups to gather naturally. In this way, we can choose not to block ourselves off from opposing views but to simply distance ourselves from them.
Nostr's relay system also allows for the opposite. Tight-knit communities can create a space for its members to socialize and exchange information with minimal interference from any outside influence. By setting up their own relays with strict rules, the members can utilize one identity to interact within a community or across the broader social network.
-
 @ b2d670de:907f9d4a
2025-03-25 20:17:57
@ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users.
Table of Contents
- Prerequisites
- Initial Server Setup
- Installing Strfry Nostr Relay
- Configuring Your Relay
- Setting Up TOR
- Making Your Relay Available on TOR
- Testing Your Setup]
- Maintenance and Security
- Troubleshooting
Prerequisites
- A Debian or Ubuntu server
- Basic familiarity with command line operations (most steps are explained in detail)
- Root or sudo access to your server
Initial Server Setup
First, let's make sure your server is properly set up and secured.
Update Your System
Connect to your server via SSH and update your system:
bash sudo apt update sudo apt upgrade -ySet Up a Basic Firewall
Install and configure a basic firewall:
bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enableThis allows SSH connections while blocking other ports for security.
Installing Strfry Nostr Relay
This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the
DEPLOYMENT.mddocument in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps here.Install Dependencies
First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry:
bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-devHere's why each dependency is needed:
Basic Development Tools: -
git: Version control system used to clone the Strfry repository and manage code updates -build-essential: Meta-package that includes compilers (gcc, g++), make, and other essential build toolsPerl Dependencies (used for Strfry's build scripts): -
libyaml-perl: Perl interface to parse YAML configuration files -libtemplate-perl: Template processing system used during the build process -libregexp-grammars-perl: Advanced regular expression handling for Perl scriptsCore Libraries for Strfry: -
libssl-dev: Development files for OpenSSL, used for secure connections and cryptographic operations -zlib1g-dev: Compression library that Strfry uses to reduce data size -liblmdb-dev: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend -libflatbuffers-dev: Memory-efficient serialization library for structured data -libsecp256k1-dev: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures -libzstd-dev: Fast real-time compression algorithm for efficient data storage and transmissionClone and Build Strfry
Clone the Strfry repository:
bash git clone https://github.com/hoytech/strfry.git cd strfryBuild Strfry:
bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores)This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime.
Install Strfry
Install the Strfry binary to your system path:
bash sudo cp strfry /usr/local/binThis makes the
strfrycommand available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions.Configuring Your Relay
Create Strfry User
Create a dedicated user for running Strfry. This enhances security by isolating the relay process:
bash sudo useradd -M -s /usr/sbin/nologin strfryThe
-Mflag prevents creating a home directory, and-s /usr/sbin/nologinprevents anyone from logging in as this user. This is a security best practice for service accounts.Create Data Directory
Create a directory for Strfry's data:
bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfryThis creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it.
Configure Strfry
Copy the sample configuration file:
bash sudo cp strfry.conf /etc/strfry.confEdit the configuration file:
bash sudo nano /etc/strfry.confModify the database path:
```
Find this line:
db = "./strfry-db/"
Change it to:
db = "/var/lib/strfry/" ```
Check your system's hard limit for file descriptors:
bash ulimit -HnUpdate the
nofilessetting in your configuration to match this value (or set to 0):```
Add or modify this line in the config (example if your limit is 524288):
nofiles = 524288 ```
The
nofilessetting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular.You might also want to customize your relay's information in the config file. Look for the
infosection and update it with your relay's name, description, and other details.Set ownership of the configuration file:
bash sudo chown strfry:strfry /etc/strfry.confCreate Systemd Service
Create a systemd service file for managing Strfry:
bash sudo nano /etc/systemd/system/strfry.serviceAdd the following content:
```ini [Unit] Description=strfry relay service
[Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000
[Install] WantedBy=multi-user.target ```
This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like
ProtectHomeandNoNewPrivileges- Sets resource limits appropriate for a relayEnable and start the service:
bash sudo systemctl enable strfry.service sudo systemctl start strfryCheck the service status:
bash sudo systemctl status strfryVerify Relay is Running
Test that your relay is running locally:
bash curl localhost:7777You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR.
Setting Up TOR
Now let's make your relay accessible as a TOR hidden service.
Install TOR
Install TOR from the package repositories:
bash sudo apt install -y torThis installs the TOR daemon that will create and manage your hidden service.
Configure TOR
Edit the TOR configuration file:
bash sudo nano /etc/tor/torrcScroll down to wherever you see a commented out part like this: ```
HiddenServiceDir /var/lib/tor/hidden_service/
HiddenServicePort 80 127.0.0.1:80
```
Under those lines, add the following lines to set up a hidden service for your relay:
HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777This configuration: - Creates a hidden service directory at
/var/lib/tor/strfry-relay/- Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR networkCreate the directory for your hidden service:
bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys.
Restart TOR to apply changes:
bash sudo systemctl restart torMaking Your Relay Available on TOR
Get Your Onion Address
After restarting TOR, you can find your onion address:
bash sudo cat /var/lib/tor/strfry-relay/hostnameThis will output something like
abcdefghijklmnopqrstuvwxyz234567.onion, which is your relay's unique .onion address. This is what you'll share with others to access your relay.Understanding Onion Addresses
The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key.
Your users will need to use this address with the WebSocket protocol prefix to connect:
ws://youronionaddress.onionTesting Your Setup
Test with a Nostr Client
The best way to test your relay is with an actual Nostr client that supports TOR:
- Open your TOR browser
- Go to your favorite client, either on clearnet or an onion service.
- Check out this list of nostr clients available over TOR.
- Add your relay URL:
ws://youronionaddress.onionto your relay list - Try posting a note and see if it appears on your relay
- In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay.
- Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected.
Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too).
Maintenance and Security
Regular Updates
Keep your system, TOR, and relay updated:
```bash
Update system
sudo apt update sudo apt upgrade -y
Update Strfry
cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry
Verify TOR is still running properly
sudo systemctl status tor ```
Regular updates are crucial for security, especially for TOR which may have security-critical updates.
Database Management
Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups.
Monitoring Logs
To monitor your Strfry logs:
bash sudo journalctl -u strfry -fTo check TOR logs:
bash sudo journalctl -u tor -fMonitoring logs helps you identify potential issues and understand how your relay is being used.
Backup
This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server.
```bash
Stop the relay temporarily
sudo systemctl stop strfry
Backup the database
sudo cp -r /var/lib/strfry /path/to/backup/location
Restart the relay
sudo systemctl start strfry ```
Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it.
bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/locationTroubleshooting
Relay Not Starting
If your relay doesn't start:
```bash
Check logs
sudo journalctl -u strfry -e
Verify configuration
cat /etc/strfry.conf
Check permissions
ls -la /var/lib/strfry ```
Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big)
TOR Hidden Service Not Working
If your TOR hidden service is not accessible:
```bash
Check TOR logs
sudo journalctl -u tor -e
Verify TOR is running
sudo systemctl status tor
Check onion address
sudo cat /var/lib/tor/strfry-relay/hostname
Verify TOR configuration
sudo cat /etc/tor/torrc ```
Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc
Testing Connectivity
If you're having trouble connecting to your service:
```bash
Verify Strfry is listening locally
sudo ss -tulpn | grep 7777
Check that TOR is properly running
sudo systemctl status tor
Test the local connection directly
curl --include --no-buffer localhost:7777 ```
Privacy and Security Considerations
Running a Nostr relay as a TOR hidden service provides several important privacy benefits:
-
Network Privacy: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay.
-
Server Anonymity: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting.
-
Censorship Resistance: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked.
-
User Privacy: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized.
However, there are some important considerations:
- TOR connections are typically slower than regular internet connections
- Not all Nostr clients support TOR connections natively
- Running a hidden service increases the importance of keeping your server secure
Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network.
For further customization and advanced configuration options, refer to the Strfry documentation.
Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network!
If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to this list. Only add it if you plan to run a stable and available relay.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 27dd78c2:66ffe658
2025-03-25 17:12:08
@ 27dd78c2:66ffe658
2025-03-25 17:12:08In an age where ‘run clubs’ are getting more popular than ‘night clubs’, it’s exciting to see a Nostr-based sovereign fitness tracker hit the scene: Enter Runstr.club!
Runstr has emerged as a game-changer, redefining how runners connect, track progress, and stay motivated. For Bitcoin Runners, a movement that advocates sovereignty of one’s wealth, while improving one’s health, Runstr.club presents an exciting platform of choice to record your proof-of-work, take ownership of your personal data, and selectively engage with your social graph.
What is Runstr.club?
Runstr.club is a platform that’s being built to grow the proof-of-work community, with plans to offer interactive leaderboards, challenges, and social engagement. Unlike traditional running apps that focus purely on statistics, Runstr.club puts emphasis on camaraderie, motivation, and shared goals. It’s the Strava alternative that values ownership of your data, interoperability between platforms, and privacy as standard.
Why Runstr.club is a Great Fit for Bitcoin Runners
Bitcoin Runners isn’t just about proof-of-work; it’s about promoting freedom tech, decentralisation, and self-sovereignty principles that align closely with the ethos of Runstr.club.
Here’s why this platform is a great match for our movement:
- Community-Driven & Decentralised Spirit
Bitcoin Runners thrives on grassroots adoption and community participation, much like Runstr.club’s organic and community-focused model. Unlike corporate-owned fitness platforms that prioritise monetisation, Runstr.club is designed to empower runners, keeping the experience authentic and meaningful.
- Privacy-First Approach
One of the key concerns for bitcoiners is privacy. Mainstream fitness platforms harvest user data for profit, but Runstr.club offers a privacy-first alternative. This makes it an excellent choice for runners who value sovereignty in the digital age.
- The Advantage of Nostr Over Centralised Run Tracking Tools
Most mainstream running apps, like Strava or Nike Run Club, rely on centralised platforms that control user data, impose restrictions, and often monetise user activity. Runstr.club, however, is built on Nostr, a decentralised protocol that enables users to interact without getting trapped inside a walled garden.
With Nostr, runners benefit from:
-
True ownership of their data – no risk of platforms selling or misusing personal running history.
-
Resilience against censorship – no arbitrary bans or content moderation dictated by a 'shadowy suit'.
-
Interoperability – seamless integration with other Nostr-based applications, keeping data fluid and accessible across different platforms.
-
Peer-to-peer connectivity – allowing runners to share progress, create challenges, and stay engaged independent of big tech.
For Bitcoin Runners, Nostr’s decentralised nature aligns perfectly with the principles of sovereignty, freedom, and privacy.
- Gamification & Challenges
Runstr.club has engaging challenges and decentralised leaderboards on its roadmap. Whether you’re stacking sats through running-related bitcoin challenges or simply competing with fellow bitcoiners for fun, the platform will add an extra layer of engagement to every run. We would love to see such features come to life!
Conclusion
Runstr.club is more than just a running tracker—it’s a Nostr, bitcoin, and fitness onboarding community-driven movement. By embracing platforms that respect privacy, encourage competition, and foster community, we stay true to our values while pushing our limits as runners.
Let’s take this to the next level - be sure to follow Runstr on Nostr!
Run free. Stay sovereign. Stack zaps!
We’re shilling this open-source initiative out of genuine appreciation for both its vision and the dedicated team behind it.
-
 @ 220522c2:61e18cb4
2025-03-25 16:05:27
@ 220522c2:61e18cb4
2025-03-25 16:05:27draftoptionalAbstract
This NIP defines a new event kind for sharing and storing code snippets. Unlike regular text notes (
kind:1), code snippets have specialized metadata like language, extension, and other code-specific attributes that enhance discoverability, syntax highlighting, and improved user experience.Event Kind
This NIP defines
kind:1337as a code snippet event.The
.contentfield contains the actual code snippet text.Optional Tags
-
filename- Filename of the code snippet -
l- Programming language name (lowercase). Examples: "javascript", "python", "rust" -
extension- File extension (without the dot). Examples: "js", "py", "rs" -
description- Brief description of what the code does -
runtime- Runtime or environment specification (e.g., "node v18.15.0", "python 3.11") -
license- License under which the code is shared (e.g., "MIT", "GPL-3.0", "Apache-2.0") -
dep- Dependency required for the code to run (can be repeated) -
repo- Reference to a repository where this code originates
Format
```json {
"id": "<32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>",
"pubkey": "<32-bytes lowercase hex-encoded public key of the event creator>",
"created_at":
, "kind": 1337,
"content": "function helloWorld() {\n console.log('Hello, Nostr!');\n}\n\nhelloWorld();",
"tags": [
["l", "javascript"], ["extension", "js"], ["filename", "hello-world.js"], ["description", "A basic JavaScript function that prints 'Hello, Nostr!' to the console"], ["runtime", "node v18.15.0"], ["license", "MIT"], ["repo", "https://github.com/nostr-protocol/nostr"]],
"sig": "<64-bytes signature of the id>"
} ```
Client Behavior
Clients that support this NIP SHOULD:
-
Display code snippets with proper syntax highlighting based on the language.
-
Allow copying the full code snippet with a single action.
-
Render the code with appropriate formatting, preserving whitespace and indentation.
-
Display the language and extension prominently.
-
Provide "run" functionality for supported languages when possible.
-
Display the description (if available) as part of the snippet presentation.
Clients MAY provide additional functionality such as:
-
Code editing capabilities
-
Forking/modifying snippets
-
Creating executable environments based on the runtime/dependencies
-
Downloading the snippet as a file using the provided extension
-
Sharing the snippet with attribution
References
nip #grownostr
-
-
 @ 220522c2:61e18cb4
2025-03-25 06:57:24
@ 220522c2:61e18cb4
2025-03-25 06:57:24
-
 @ 0d6c8388:46488a33
2025-03-28 16:24:00
@ 0d6c8388:46488a33
2025-03-28 16:24:00Huge thank you to OpenSats for the grant to work on Hypernote this year! I thought I'd take this opportunity to try and share my thought processes for Hypernote. If this all sounds very dense or irrelevant to you I'm sorry!
===
How can the ideas of "hypermedia" benefit nostr? That's the goal of hypernote. To take the best ideas from "hypertext" and "hypercard" and "hypermedia systems" and apply them to nostr in a specifically nostr-ey way.
1. What do we mean by hypermedia
A hypermedia document embeds the methods of interaction (links, forms, and buttons are the most well-known hypermedia controls) within the document itself. It's including the how with the what.
This is how the old web worked. An HTML page was delivered to the web browser, and it included in it a link or perhaps a form that could be submitted to obtain a new, different HTML page. This is how the whole web worked early on! Forums and GeoCities and eBay and MySpace and Yahoo! and Amazon and Google all emerged inside this paradigm.
A web browser in this paradigm was a "thin" client which rendered the "thick" application defined in the HTML (and, implicitly, was defined by the server that would serve that HTML).
Contrast this with modern app development, where the what is usually delivered in the form of JSON, and then HTML combined with JavaScript (React, Svelte, Angular, Vue, etc.) is devised to render that JSON as a meaningful piece of hypermedia within the actual browser, the how.
The browser remains a "thin" client in this scenario, but now the application is delivered in two stages: a client application of HTML and JavaScript, and then the actual JSON data that will hydrate that "application".
(Aside: it's interesting how much "thicker" the browser has had to become to support this newer paradigm!)
Nostr was obviously built in line with the modern paradigm: nostr "clients" (written in React or Svelte or as mobile apps) define the how of reading and creating nostr events, while nostr events themselves (JSON data) simply describe the what.
And so the goal with Hypernote is to square this circle somehow: nostr currently delivers JSON what, how do we deliver the how with nostr as well. Is that even possible?
2. Hypernote's design assumptions
Hypernote assumes that hypermedia over nostr is a good idea! I'm expecting some joyful renaissance of app expression similar to that of the web once we figure out how to express applications in a truly "nostr" way.
Hypernote was also deeply inspired by HTMX, so it assumes that building web apps in the HTMX style is a good idea. The HTMX insight is that instead of shipping rich scripting along with your app, you could simply make HTML a tiny bit more expressive and get 95% of what most apps need. HTMX's additions to the HTML language are designed to be as minimal and composable as possible, and Hypernote should have the same aims.
Hypernote also assumes that the "design" of nostr will remain fluid and anarchic for years to come. There will be no "canonical" list of "required" NIPs that we'll have "consensus" on in order to build stable UIs on top of. Hypernote will need to be built responsive to nostr's moods and seasons, rather than one holy spec.
Hypernote likes the
nakcommand line tool. Hypernote likes markdown. Hypernote likes Tailwind CSS. Hypernote likes SolidJS. Hypernote likes cold brew coffee. Hypernote is, to be perfectly honest, my aesthetic preferences applied to my perception of an opportunity in the nostr ecosystem.3. "What's a hypernote?"
Great question. I'm still figuring this out. Everything right now is subject to change in order to make sure hypernote serves its intended purpose.
But here's where things currently stand:
A hypernote is a flat list of "Hypernote Elements". A Hypernote Element is composed of:
- CONTENT. Static or dynamic content. (the what)
- LOGIC. Filters and events (the how)
- STYLE. Optional, inline style information specific to this element's content.
In the most basic example of a hypernote story, here's a lone "edit me" in the middle of the canvas:

{ "id": "fb4aaed4-bf95-4353-a5e1-0bb64525c08f", "type": "text", "text": "edit me", "x": 540, "y": 960, "size": "md", "color": "black" }As you can see, it has no logic, but it does have some content (the text "edit me") and style (the position, size, and color).
Here's a "sticker" that displays a note:
{ "id": "2cd1ef51-3356-408d-b10d-2502cbb8014e", "type": "sticker", "stickerType": "note", "filter": { "kinds": [ 1 ], "ids": [ "92de77507a361ab2e20385d98ff00565aaf3f80cf2b6d89c0343e08166fed931" ], "limit": 1 }, "accessors": [ "content", "pubkey", "created_at" ], "x": 540, "y": 960, "associatedData": {} }As you can see, it's kind of a mess! The content and styling and underdeveloped for this "sticker", but at least it demonstrates some "logic": a nostr filter for getting its data.
Here's another sticker, this one displays a form that the user can interact with to SEND a note. Very hyper of us!
{ "id": "42240d75-e998-4067-b8fa-9ee096365663", "type": "sticker", "stickerType": "prompt", "filter": {}, "accessors": [], "x": 540, "y": 960, "associatedData": { "promptText": "What's your favorite color?" }, "methods": { "comment": { "description": "comment", "eventTemplate": { "kind": 1111, "content": "${content}", "tags": [ [ "E", "${eventId}", "", "${pubkey}" ], [ "K", "${eventKind}" ], [ "P", "${pubkey}" ], [ "e", "${eventId}", "", "${pubkey}" ], [ "k", "${eventKind}" ], [ "p", "${pubkey}" ] ] } } } }It's also a mess, but it demos the other part of "logic": methods which produce new events.
This is the total surface of hypernote, ideally! Static or dynamic content, simple inline styles, and logic for fetching and producing events.
I'm calling it "logic" but it's purposfully not a whole scripting language. At most we'll have some sort of
jq-like language for destructing the relevant piece of data we want.My ideal syntax for a hypernote as a developer will look something like
```foo.hypernote Nak-like logic
Markdown-like content
CSS-like styles ```
But with JSON as the compile target, this can just be my own preference, there can be other (likely better!) ways of authoring this content, such as a Hypernote Stories GUI.
The end
I know this is all still vague but I wanted to get some ideas out in the wild so people understand the through line of my different Hypernote experiments. I want to get the right amount of "expressivity" in Hypernote before it gets locked down into one spec. My hunch is it can be VERY expressive while remaining simple and also while not needing a whole scripting language bolted onto it. If I can't pull it off I'll let you know.
-
 @ 4259e401:8e20e9a6
2025-03-24 14:27:27
@ 4259e401:8e20e9a6
2025-03-24 14:27:27[MVP: Gigi! How do I lightning prism this?]
If I could send a letter to myself five years ago, this book would be it.
I’m not a Bitcoin expert. I’m not a developer, a coder, or an economist.
I don’t have credentials, connections, or capital.
I’m a blue-collar guy who stumbled into Bitcoin almost exactly four years ago, and like everyone else, I had to wrestle with it to understand it.
Bitcoin is one of the most misunderstood, misrepresented, and misinterpreted ideas of our time - not just because it’s complex, but because its very structure makes it easy to distort.
It’s decentralized and leaderless, which means there’s no single voice to clarify what it is or defend it from misinformation.
That’s a feature, not a bug, but it means that understanding Bitcoin isn’t easy.
It’s a system that doesn’t fit into any of our existing categories. It’s not a company. It’s not a product. It’s not a government.
There’s no marketing department, no headquarters, no CEO.
That makes it uniquely resistant to corruption, but also uniquely vulnerable to disinformation.
Whether through negligence or malice, Bitcoin is constantly misunderstood - by skeptics who think it’s just a Ponzi scheme, by opportunists looking to cash in on the hype, by scammers who use the name to push worthless imitations, and by critics who don’t realize they’re attacking a strawman.
If you’re new to Bitcoin, you have to fight through layers of noise before you can even see the signal.
And that process isn’t instant.
Even if you could explain digital signatures off the top of your head, even if you could hash SHA-256 by hand, even if you had a perfect technical understanding of every moving part - you still wouldn’t get it.
Bitcoin isn’t just technology. It’s a shift in incentives, a challenge to power, an enforcer of sovereignty. It resists censorship.
A simple open ledger - yet it shakes the world.
Archimedes asked for a lever and a place to stand, and he could move the world.
Satoshi gave us both.
The lever is Bitcoin - an economic system with perfect game theory, incorruptible rules, and absolute scarcity.
The place to stand is the open-source, decentralized network, where anyone can verify, participate, and build without permission.
And what comes out of this seemingly simple equation?
The entire rearchitecture of trust. The separation of money and state.
A foundation upon which artificial intelligence must negotiate with the real world instead of manipulating it.
A digital economy where energy, computation, and value flow in perfect symmetry, refining themselves in an endless virtuous cycle.
Bitcoin started as a whitepaper.
Now it’s a lifeline, an immune system, a foundation, a firewall, a torch passed through time.
From such a small set of rules - 21 million divisible units, cryptographic ownership, and a fixed issuance schedule - emerges something unstoppable.
Something vast enough to absorb and constrain the intelligence of machines, to resist the distortions of human greed, to create the rails for a world that is freer, more sovereign, more aligned with truth than anything that came before it.
It’s proof that sometimes, the most profound revolutions begin with the simplest ideas. That’s why this book exists.
Bitcoin isn’t something you learn - it’s something you unlearn first.
You start with assumptions about money, value, and authority that have been baked into you since birth. And then, piece by piece, you chip away at them.
It’s like peeling an onion – it takes time and effort.
*And yes, you might shed some tears! *
At first, you might come for the speculation. A lot of people do. But those who stay - who actually take the time to understand what’s happening - don’t stay for the profits.
They stay for the principles.
If you’re holding this book, you’re somewhere on that journey.
Maybe you’re at the very beginning, trying to separate the signal from the noise.
Maybe you’ve been down the rabbit hole for years, looking for a way to articulate what you already know deep in your bones.
Either way, this is for you.
It’s not a technical manual, and it’s not a sales pitch. It’s the book I wish I had when I started.
So if you’re where I was, consider this a message in a bottle, thrown back through time. A hand reaching through the fog, saying:
“Keep going. It’s worth it.”
Preface The End of The Beginning
March 2025.
The moment has arrived. Most haven’t even noticed, let alone processed it. The United States is setting up a Bitcoin (Bitcoin-only!) strategic reserve.
It’s not a theory. Not an idea. The order is signed, the ink is dried.
The people who have been wrong, over and over (and over!) again - for years! - fumble for explanations, flipping through the wreckage of their previous predictions:
“Bubble…’’ “Fad…” “Ponzi…”
No longer.
The same analysts who once sneered are now adjusting their forecasts to protect what’s left of their credibility. Those who dismissed it are now trapped in a slow, humiliating realization: Bitcoin does not require their approval.
It never did.
Something fundamental has shifted, and the air is thick with a paradoxical cocktail of triumph and panic. Bitcoiners saw this coming. Not because they had insider information, but because they understood first principles when everyone else was still playing pretend.
Bitcoin was never just surviving.
It was infiltrating.
The question is no longer whether Bitcoin will succeed.
It already has.
The only question that remains is who understands, and who is still in denial.
Think back to 2022.
At its peak, FTX was one of the world’s largest cryptocurrency exchanges, valued at $32 billion and backed by blue-chip investors. It promised a sophisticated, institutional-grade trading platform, attracting retail traders, hedge funds, and politicians alike. Sam Bankman-Fried, with his disheveled hair and cargo shorts, was its eccentric figurehead, a billionaire who slept on a bean bag and spoke of philanthropy.
Then the illusion shattered.
FTX collapsed overnight, an implosion so violent it left an entire industry scrambling for cover. One moment, Sam Bankman-Fried was the golden boy of crypto - genius quant, regulatory darling, effective altruist™.
The next, he was just another fraudster in handcuffs.
Billions vanished. Customers locked out. Hedge funds liquidated.
Politicians who had once taken photos with SBF and smiled at his political donations, suddenly pretended they had no idea who he was. The same regulators who were supposed to prevent disasters like this stood slack-jawed, acting as if they hadn’t been having closed-door meetings with FTX months before the collapse.
But FTX wasn’t just a scandal, it was a filter.
If you were Bitcoin-only, with your satoshis in cold storage, you didn’t even flinch. From your perspective, nothing important changed:
A new Bitcoin block still arrived every ten minutes (on average). The supply cap of 21 million bitcoins remained untouched. Ownership was still protected by public/private key cryptography.
You were literally unaffected.
You had already updated your priors:
“If you don’t hold your own keys, you own nothing.” “Bitcoin is not ‘crypto’.” “’Crypto’ is a casino.”
FTX was just another financial fire, another chapter in the never-ending saga of people trusting systems that had already proven themselves untrustworthy.
That moment was a prelude.
The U.S. Bitcoin pivot is the paradigm shift.
The Eukaryotic Revolution Is Upon Us
In biology, abiogenesis is when life emerged from non-life - a fragile, uncertain process where the first microscopic self-replicators struggled to survive against hostile conditions. That was Bitcoin’s early history. It had to fight for its existence, attacked by governments, dismissed by economists, ridiculed by mainstream media.
But it survived.
That era is over. We have entered the Eukaryotic Revolution.
This is the moment in evolutionary history when simple lifeforms evolved into something structurally complex - organisms with nuclei, internal scaffolding, and the ability to form multicellular cooperatives and populate diverse ecosystems. Once this transformation happened, there was no going back. Bitcoin is going through its own Eukaryotic leap.
Once an outsider, dismissed and ridiculed, it is maturing into an integrated, resilient force within the global financial system.
On March 2, 2025, the Trump administration announced a Crypto Strategic Reserve.
At first, it wasn’t just Bitcoin - it included XRP, SOL, and ADA, a desperate attempt to appease the altcoin industry. A political move, not an economic one.
For about five minutes, the broader crypto industry cheered. Then came the pushback.
Bitcoiners called it immediately: mixing Bitcoin with centralized altcoin grifts was like adding lead weights to a life raft.
Institutional players rejected it outright: sovereign reserves need hard assets, not tech company tokens. The government realized, almost immediately, that it had made a mistake.
By March 6, 2025, the pivot was complete.
Strategic Bitcoin reserve confirmed. The President signed an executive order, and legislation has been introduced in the United States House of Representatives.
The U.S. government’s official bitcoin policy: hold, don’t sell. Look for ways to acquire more.
Altcoins relegated to second-tier status, treated as fundamentally separate from and inferior to bitcoin. The government’s official policy: sell, and do not actively accumulate more (ouch!).
“Bitcoin maximalism” – the belief that any cryptocurrency other than bitcoin lies on a spectrum between “bad idea” and outright scam - wasn’t vindicated by debate.
It was vindicated by economic reality.
When the government was forced to choose what belonged in a sovereign reserve, it wasn’t even close. Bitcoin stood alone.
“There is no second best.” -Michael Saylor
Who This Book Is For: The Three Types of Readers
You’re here for a reason.
Maybe you felt something shift.
Maybe you saw the headlines, sensed the undercurrents, or simply couldn’t ignore the growing drumbeat any longer.
Maybe you’ve been here all along, waiting for the world to catch up.
Whatever brought you to this book, one thing is certain: you’re curious enough to learn more.
Bitcoin forces a reevaluation of assumptions - about money, trust, power, and the very foundations of the economic order. How much of that process you’ve already undergone will determine how you read these pages.
1. The Layperson → new, curious, maybe skeptical. Bitcoin probably looks like chaos to you right now. One person says it’s the future. Another says it’s a scam. The price crashes. The price doubles. The news is either breathless excitement or total doom. How the hell are you supposed to figure this out?
If that’s you, welcome.
This book was built for you.
You don’t need to be an economist, a technologist, or a finance geek to understand what’s in these pages. You just need an open mind and the willingness to engage with new ideas - ideas that will, if you follow them far enough, challenge some of your deepest assumptions.
Bitcoin is not an investment. Bitcoin is not a company. Bitcoin is not a stock, a trend, or a passing phase.
Bitcoin is a paradigm shift. And by the time you reach the last page, you won’t need to be convinced of its importance. You’ll see it for yourself.
2. The Student → understand the basics, want to go deeper.
You’ve already stepped through the door.
You’ve realized Bitcoin is more than just digital gold. You understand decentralization, scarcity, censorship resistance… But the deeper you go, the more you realize just how much there is to understand.
3. The Expert → You’ve been in the game for years.
You’ve put in the time.
You don’t need another book telling you Bitcoin will succeed. You already know.
You’re here because you want sharper tools.
Tighter arguments.
A way to shut down nonsense with fewer words, and more force.
Maybe this book will give you a new way to frame an idea you’ve been struggling to convey.
Maybe it will help you refine your messaging and obliterate some lingering doubts in the minds of those around you.
Or maybe this will simply be the book you hand to the next person who asks, “Okay… but what’s the deal with Bitcoin?” so you don’t have to keep explaining it from scratch.
*If you’re already deep in the weeds, you can probably skip Part I (Foundations) without missing much - unless you’re curious about a particular way of putting a particular thing. *
Part II (Resilience) is where things get more interesting. Why you want to run a node, even if you don’t know it yet. The energy debate, stripped of media hysteria. The legend of Satoshi, and what actually matters about it.
If you’re a hardcore cypherpunk who already speaks in block heights and sending Zaps on NOSTR, feel free to jump straight to Part III (The Peaceful Revolution). Chapter 15, “The Separation of Money and State” is where the gloves come off.
Bitcoin isn’t just a technology. Bitcoin isn’t just an economic movement. Bitcoin is a lens.
And once you start looking through it, the world never looks the same again.
This book will teach you what Bitcoin is, as much as it will help you understand why Bitcoiners think the way they do.
It isn’t just something you learn about.
Especially not in one sitting, or from one book.
It’s something you grow to realize.
Regardless of which category you fall into, you’ve already passed the first test.
You’re still reading.
You haven’t dismissed this outright. You haven’t scoffed, rolled your eyes, or walked away. You’re at least curious.
And that’s all it takes.
Curiosity is the only filter that matters.
The rest takes care of itself.
The Essential Role of Memes Memes won the narrative war - it wasn’t textbooks, research papers, or whitepapers that did it. Bitcoin spread the same way evolution spreads successful genes - through replication, variation, and selection. Richard Dawkins coined the term “meme” in The Selfish Gene, describing it as a unit of cultural transmission - behaving much like a gene. Memes replicate, mutate, and spread through culture. Just as natural selection filters out weak genes, memetic selection filters out weak ideas.
But Bitcoin memes weren’t just jokes.
They were premonitions.
The most powerful ideas are often compact, inarguable, and contagious - and Bitcoin’s memes were all three. They cut through complexity like a scalpel, distilling truths into phrases so simple, so undeniable, that they burrowed into the mind and refused to leave.
"Bitcoin fixes this." "Not Your Keys, Not Your Coins." "Number Go Up."
Each of these is more than just a slogan.
They’re memetic payloads, compressed packets of truth that can carry everything you need to understand about Bitcoin in just a few words.
They spread through conversations, through tweets, through shitposts, through relentless repetition.
They bypassed the gatekeepers of financial knowledge, infecting minds before Wall Street even understood what was happening.
And they didn’t just spread.
They reshaped language itself.
Before Bitcoin, the word fiat was a sterile economic term, borrowed from Latin, meaning "by decree." It had no weight, no controversy - just a neutral descriptor for government-issued money.
But Bitcoiners forced a memetic shift.
They didn’t just make fiat mainstream.
**They made it radioactive. **
They stripped away the academic detachment and revealed its true essence:
money because I said so.
No backing. No inherent value.
Just a command.
And of course, an unspoken threat -
"Oh, and by the way, I have a monopoly on violence, so you’d better get on board."
This wasn’t just linguistic evolution; it was a memetic coup.
Bitcoiners took a sterile term and injected it with an unavoidable truth: fiat money exists not because it is chosen, but because it is imposed.
Central banks, governments, and financial institutions now use the term fiat without a second thought.
The meme has done its work.
A word that was once neutral, now carries an implicit critique - a quiet but persistent reminder that there is an alternative.
Bitcoin didn’t just challenge the financial system - it rewired the language we use to describe it.
“Money printer go BRRRRRR" did more damage to the Fed’s reputation than a thousand Austrian economics treatises ever could.
Memes exposed what balance sheets and policy reports tried to obscure. They turned abstract economic forces into something visceral, something undeniable.
And now - they are historical markers of the shift, the fossil record of our collective consciousness coming to terms with something fundamentally new in the universe.
The old world relied on authority, institutional credibility, and narrative control.
Bitcoin broke through with memes, first principles, and lived experience.
This wasn’t just an ideological battle.
It was an evolutionary process.
The weaker ideas died. The strongest ones survived.
Once a meme - in other words, an idea - takes hold, there is nothing - no law, no regulation, no institution, no government - that can stop it.
Bitcoin exists. It simply is.
And it will keep producing blocks, every ten minutes, whether you get it or not.
This book isn’t a trading manual.
It won’t teach you how to time the market, maximize your gains, or set up a wallet.
It’s a carefully curated collection of memes, giving you the prerequisite mental scaffolding to grok the greatest monetary shift in human history.
A shift that has already begun.
The only thing to decide is whether you’re watching from the sidelines or whether you’re part of it.
The rest is up to you.
How This Book Is Structured Bitcoin spreads like an evolutionary force - through memes. Each chapter in this book isn’t just an idea, it’s a memetic payload, designed to install the concepts that make Bitcoin inevitable. The book is broken into three phases:
*I. Foundations *** Memes as Mental Antivirus The first layer cuts through noise and filters out distractions. "Bitcoin Only" is the first test - if you get this one wrong, you waste years chasing ghosts. "Don’t Trust, Verify" rewires how you think about truth. And "Not Your Keys, Not Your Coins"? If you learn it the hard way, it’s already too late.
II. Resilience Memes as Weapons in the Information War Here’s where Bitcoin earns its survival. "Shitcoiners Get REKT" is a law, not an opinion. "Fork Around and Find Out" proves that you don’t change Bitcoin - Bitcoin changes you. "Antifragile, Unstoppable" shows how every attack on Bitcoin has only made it stronger.
III. The Peaceful Revolution ** Memes as Reality Distortion Fields By now, Bitcoin isn’t just an asset - it’s a lens. "Separation of Money and State" isn’t a theory; it’s happening in real time. "Fix the Money, Fix the World" isn’t a slogan; it’s a diagnosis. And "Tick Tock, Next Block"? No matter what happens, Bitcoin keeps producing blocks.
These aren’t just memes. They’re scaffolding for a new way of thinking. Each one embeds deeper until you stop asking if Bitcoin will succeed - because you realize it already has.
Next: Chapter 1: Bitcoin Only. ** For now, it’s a heuristic - an efficient filter that separates signal from noise, with minimal effort.
But by the time you finish this book, it won’t be a heuristic anymore.
It will be something you know.Welcome to the rabbit hole.
-
 @ a012dc82:6458a70d
2025-03-28 16:15:06
@ a012dc82:6458a70d
2025-03-28 16:15:06In an audacious display of confidence, Bitcoin traders have recently committed $20 million to a $200K call option, a move that has reignited discussions about the cryptocurrency's potential and the broader market's appetite for risk. This development is set against a backdrop of increasing activity within the cryptocurrency options market, particularly on platforms like Deribit, where total open interest in Bitcoin options has reached unprecedented levels. This article explores the nuances of this strategic wager, examines the resurgence of investor enthusiasm, and contemplates the future implications for Bitcoin and the cryptocurrency market at large.
Table of Contents
-
A Surge in Market Activity
-
The Bold Bet on Bitcoin's Future
-
Implications of the $200K Call Option
-
Increased Market Volatility
-
Renewed Investor Confidence
-
Speculative Interest and Market Dynamics
-
-
Looking Ahead: Bitcoin's Market Prospects
-
Conclusion
-
FAQs
A Surge in Market Activity
The cryptocurrency options market has experienced a significant uptick in activity, with Bitcoin and Ethereum options achieving record-breaking open interest figures. On Deribit, Bitcoin options open interest has soared to a staggering $20.4 billion, eclipsing the previous high of $14.36 billion seen in October 2021. Concurrently, Ethereum options open interest has also reached a historic peak of $11.66 billion. This pronounced increase in market activity is indicative of a growing interest among traders to either hedge their positions against potential price fluctuations or to speculate on the future price movements of these leading cryptocurrencies. The surge in options trading volume reflects a broader trend of maturation within the cryptocurrency market, as sophisticated financial instruments become increasingly utilized by a diverse array of market participants, from individual investors to large institutional players.
The Bold Bet on Bitcoin's Future
The decision by traders to allocate $20 million to a $200K call option for Bitcoin represents a significant vote of confidence in the cryptocurrency's future price trajectory. This high-stakes gamble suggests that a segment of the market is not only optimistic about Bitcoin's potential to breach the $200,000 threshold but is also willing to back this belief with substantial financial commitment. Such a move is emblematic of the "animal spirits" returning to the cryptocurrency market—a term coined by economist John Maynard Keynes to describe the instinctive human emotion that drives consumer confidence and investment decisions. This resurgence of speculative fervor and risk-taking behavior is a testament to the enduring allure of Bitcoin as an asset class that continues to captivate the imagination of investors, despite its history of volatility and regulatory challenges.
Implications of the $200K Call Option
The substantial investment in the $200K call option carries several implications for the Bitcoin market and the broader cryptocurrency ecosystem:
Increased Market Volatility
The focus on high strike price options could introduce heightened volatility into the Bitcoin market. As traders position themselves to capitalize on potential price movements, the market may witness more pronounced fluctuations. This environment of increased volatility underscores the speculative nature of cryptocurrency trading and the high-risk, high-reward strategies employed by some market participants. It also highlights the need for investors to approach the market with caution, armed with a thorough understanding of the underlying risks and a clear investment strategy.
Renewed Investor Confidence
The bold wager on the $200K call option reflects a significant resurgence in investor confidence in Bitcoin's long-term prospects. Following periods of market downturns and regulatory uncertainty, this move signals a renewed conviction in the fundamental value proposition of Bitcoin as a pioneering digital asset. It represents a collective belief in the cryptocurrency's ability to not only recover from past setbacks but to chart new territories in terms of price and market capitalization. This renewed investor confidence may serve as a catalyst for further investment in Bitcoin and other cryptocurrencies, potentially driving up prices and encouraging more widespread adoption.
Speculative Interest and Market Dynamics
The commitment to the $200K call option highlights the continued influence of speculative interest on the cryptocurrency market's dynamics. It illustrates how speculation, driven by the prospect of outsized returns, remains a central force shaping market trends and price trajectories. This speculative interest, while contributing to market liquidity and price discovery, also introduces an element of unpredictability. It underscores the complex interplay between market sentiment, investor behavior, and external economic factors that collectively determine the direction of the cryptocurrency market.
Looking Ahead: Bitcoin's Market Prospects
The strategic bet on the $200K call option, amidst a backdrop of increasing options market activity, paints a complex picture of Bitcoin's future. While the move signals optimism and a willingness among investors to engage in high-risk speculation, it also raises questions about the sustainability of such bullish sentiment. As Bitcoin continues to navigate the evolving landscape of digital finance, the interplay between speculative interest, regulatory developments, and technological advancements will be critical in shaping its future trajectory. The cryptocurrency market's inherent volatility and unpredictability necessitate a cautious approach from investors, emphasizing the importance of risk management and long-term strategic planning.
Conclusion
Bitcoin's latest foray into high-stakes speculation, marked by the $20 million lock on the $200K call option, is a vivid illustration of the cryptocurrency's enduring appeal and the market's appetite for risk. This development not only reflects a bullish outlook on Bitcoin's price potential but also signals a broader resurgence of investor enthusiasm and speculative activity within the cryptocurrency market. As we look to the future, the outcomes of such bold moves will undoubtedly influence the trajectory of Bitcoin and the digital asset landscape at large. Whether Bitcoin will reach the lofty heights of $200,000 remains to be seen, but its journey there will be closely watched by traders, investors, and regulators alike, offering valuable insights into the dynamics of speculative markets and the evolving role of cryptocurrencies in the global financial ecosystem.
FAQs
What does locking $20 million in a $200K call option mean for Bitcoin? Locking $20 million in a $200K call option indicates that traders are betting a significant amount of money on Bitcoin reaching or surpassing $200,000. It reflects a bullish outlook on Bitcoin's future price and a resurgence of speculative interest in the cryptocurrency market.
How does the surge in Bitcoin options market activity affect the cryptocurrency? The surge in Bitcoin options market activity, with record open interest, increases market liquidity and can lead to heightened volatility. It also signifies growing interest and participation in the cryptocurrency market, potentially influencing Bitcoin's price dynamics.
What are the implications of increased market volatility for Bitcoin investors? Increased market volatility can lead to larger price swings, presenting both opportunities and risks for investors. While it may offer the potential for higher returns, it also increases the risk of losses. Investors should approach the market with caution and consider their risk tolerance and investment strategy.
Why are investors optimistic about Bitcoin reaching $200,000? Investors' optimism about Bitcoin reaching $200,000 stems from factors such as the cryptocurrency's past performance, the upcoming Bitcoin halving event, increasing institutional adoption, and favorable macroeconomic conditions. These factors contribute to a bullish sentiment in the market.
What role do institutional investors play in the current Bitcoin market trend? Institutional investors play a significant role in the current Bitcoin market trend by bringing in substantial capital, lending credibility to the market, and influencing price movements. Their participation is seen as a sign of maturity and stability in the cryptocurrency market.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ bf95e1a4:ebdcc848
2025-03-28 13:56:06
@ bf95e1a4:ebdcc848
2025-03-28 13:56:06This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
Financial Atheism
“Don’t trust, verify” is a common saying amongst bitcoiners that represents a sound attitude towards not only Bitcoin but all human power structures. In order to understand Bitcoin, one must admit that everything in society is man-made. Every civilization, every religion, every constitution, and every law is a product of human imagination. It wasn’t until as late as the 17th century that the scientific method started to become the dominant practice for describing how the world actually worked. Peer-to-peer review and repeated testing of a hypothesis are still quite recent human practices. Before this, we were basically just guessing and trusting authorities to a large extent. We still do this today, and despite our progress over the last couple of centuries, we still have a long way to go. Our brains are hardwired to follow the leader of the pack. The human brain is born with a plethora of cognitive biases pre-installed, and we have to work very hard to overcome them. We evolved to survive in relatively small groups, and our brains are thus not really made for seeing the bigger picture. Bitcoin’s proof-of-work algorithm is constructed in such a way that it is easy to verify that computational power was sacrificed in order to approve a block of transactions and claim its reward. In this way, no trust in any authority is required as it is relatively trivial to test the validity of a block and the transactions it contains. This is nothing short of a complete reimagining of how human society ought to be governed. The beauty of mathematics governs the Bitcoin system. Everything that ever happens in Bitcoin is open and verifiable to everyone, even to those who are not yet using it.
After the tragic events of 9/11 in 2001, Sam Harris started writing his book The End of Faith, which happened to be released around the same time as Richard Dawkins’ The God Delusion, Daniel Dennett's Breaking the Spell, and Christopher Hitchens’ God Is Not Great: How Religion Poisons Everything. These books kick-started what, in hindsight, has often been referred to as the new atheist movement, even though there has arguably never been anything new about atheism. Atheism must almost certainly have preceded religion since religious ideas require the person holding the idea to believe a certain doctrine or story. Atheism is nothing but the rejection of ways to describe the world that are not verifiable by experimentation. A fly on the wall is probably an atheist by this definition of the word. Atheism is often accused of being just another set of beliefs, but the word itself describes what it is much better — a lack of belief in theistic ideas. It is not a code of conduct or set of rules to live your life by; it is simply the rejection of that which cannot be scientifically verified. Many people, religious people, in particular, have a hard time grasping this. If you believe that a supernatural entity created everything in everyone's life, you might not be too comfortable with a word that describes a complete rejection of what you believe created everything, including the very atheist that the word describes. The amount of different religious worldviews that exist is probably equal to the sum of all religious people on the planet, but all world views that reject these superstitious beliefs require but one word. Atheism is not the opposite of religion but is simply the lack of it.
In 2008, another sub-culture movement of unbelief was born. Let’s call it Financial Atheism — the rejection of unverifiable value claims. With the invention of Bitcoin, a way of rejecting fraudulent expressions of a token’s value was born. Those of us fortunate enough to have been born in secular countries all enjoy not having the ideas of religious demagogues dictating our lives on a daily basis. We can choose which ideas to believe in and which to reject. What we still have very limited means of choosing, however, are the ways in which we express value to each other. We’re told to use a system in which we all have a certain number of value tokens assigned to our name, either as a number on a screen or as digits on paper notes. We all live in the collective hallucination that these numbers are somehow legit and that their authenticity is not to be questioned.
A Bitcoin balance assigned to a certain Bitcoin address might seem just as questionable to a layman, but if you have a basic understanding of the hashing algorithms and game theory behind it, it’s not. At the time of writing, the hash of the latest block on the Bitcoin blockchain begins with eighteen zeros in a row. These zeros represent the Proof of Work that ensures that this block is valid and that every transaction in it actually happened. If you can grasp the concept of a hashing algorithm, and if you have an intuition about mathematics, you realize the gargantuan amount of calculating effort that went into finding this particular hash. It is simply mind-blowing. To forge a false version of a hash beginning with eighteen zeros just wouldn’t be economically viable. Of course, you can never actually know that a 51% attack or some other attempt at corrupting the blockchain hasn’t occurred, but you can know that such an attack would require more than half of the network acting against their own economic interest. Bitcoin is not something to believe in. You don’t need to trust any authority because you can validate the plausibility of its authenticity yourself. It’s the financial equivalent of atheism or unbelief. Satoshi wasn’t Jesus. Satoshi was Brian of Nazareth, telling his followers to think for themselves.
The first law of thermodynamics, also known as the Law of Conservation of Energy, states that energy cannot be created or destroyed in an isolated system. The second law states that the entropy of any isolated system always increases, and the third law states that the entropy of a system approaches a constant value as the temperature approaches absolute zero. In the Bitcoin network, participants known as miners compete for new Bitcoin in a lottery with very fixed rules. The more hashing power (computing power) a miner contributes to the network, the higher his chances of winning the block reward, a specific amount of Bitcoin that is halved every four years. The difficulty of this lottery - in other words, the miner’s chance of winning it — is re-calibrated every 2016th block so that the average time it takes to find the next block is always roughly ten minutes. What this system produces is absolute scarcity; the amount of Bitcoin in existence at any moment in time is always predictable. The more time that passes, the slower the rate of coin issuance and the block reward slowly approaches zero. By the time it does, around the year 2140, the individual miner’s incentive to mine for a reward will, at least theoretically, have been replaced by an incentive to collect transaction fees from the participants of the network. Even now, the sum of all fees make up a non-trivial part of the miners’ revenue. Yet from a user’s point of view the fees are still very low, and as the network scales up using Layer 2 solutions such as the Lightning Network, they’re expected to remain low for quite a long time ahead.
Absolute scarcity is a concept that mankind has never encountered before. Arguably, this makes it the first man-made concept to ever be directly linked to the laws of physics. Everything anyone does requires a certain amount of energy. The very word doing implies that some kind of movement, some type of energy expenditure, needs to occur. As mentioned earlier, how we value things is entirely subjective. Different actions are of different value to different people. How we value different things is also inevitably linked to the supply of those things. Had the trapped-under-ice winter diver mentioned in chapter one been equipped with a scuba tank, he probably wouldn't have thought of his next breath as such a precious thing. The price a person is willing to pay for a good — in other words, the sum of one or more person’s actions — can be derived from two basic variables: The highly subjective demand for the good and the always-constrained-by-time-and-space supply of that same good. Note that if supply is sufficiently limited, there only needs to be a minimal amount of demand for a good for its price to increase.
One could argue that no one needs Bitcoin and that, therefore, Bitcoin would have no intrinsic value. One could also argue that there’s no such thing as intrinsic value since demand is always subjective. In any case, there will always be a cost to mine Bitcoin, and the more mining power in the network, the higher that cost. This cost, ensured by the Bitcoin network’s Proof-Of-Work algorithm, is probably as close to a pure energy cost as the price of a human activity will ever get. Once the mining rig is in place, a simple conversion process follows — energy in, scarce token out. Should the cost of production exceed the current price of the token, the miner can just choose not to sell, thereby limiting the supply of Bitcoin in circulation even more and eventually selling them for other goods whenever he sees fit. In this sense, Bitcoin is a battery. Perhaps the best battery ever invented.
Storing and moving electrical energy around has always been costly and wasteful. Bitcoin offers a way of converting energy into a small part of a specific number. A mathematical battery, if you will. It is important to remember that it does not convert energy into value directly, but rather electricity into digital scarcity — digital scarcity that can be used to express value. Energy cannot be created or destroyed in an isolated system, as the first law of thermodynamics clearly states. Bitcoin can express how much energy was sacrificed in order to acquire a share of the total sum. You can also acquire Bitcoin by buying it rather than mining it, but in doing so, you also spend energy. You somehow acquired the money with which you bought the Bitcoin. You, or someone else, sacrificed time and energy somewhere. Bitcoin lets you express that you see that there’s a connection between value and scarcity by letting you sacrifice effort to claim a part of the total sum.
The excitement we so-called "Bitcoin Maximalists" feel about Bitcoin does not come primarily from the enormous gains that those who hopped early onto the freight train have been blessed with. Nor is it because we’re “in it for the technology,” as can often be heard from opponents. Those of us who preach the near-divinity of this invention do so above all because we see the philosophical impacts of absolute scarcity in a commodity. The idea of a functioning solution to the double-spending problem in computerized money is an achievement that simply can’t be ignored. By solving the double-spending problem, Satoshi also made counterfeiting impossible, which in turn makes artificial inflation impossible. The world-changing potential of this invention cannot be understated. Not in the long run.
The more you think about it, the more the thought won’t give you any peace of mind. If this experiment works, if it’s real, it will take civilization to the next level. What we don’t know is how long this will take. Right now, debates in the Bitcoin space are about Bitcoin’s functionality as a medium of exchange and its potential as a good store of value. We might be missing the point. We cannot possibly know if a type of monetary token for which you’re completely responsible, with no third-party protection, will ever become a preferred medium of exchange for most transactions. Nor can we know if the price of Bitcoin will follow the hype-cycle path that we all want it to follow so that it can become the store of value that most maximalists claim it already is. Maybe we’ve been focused on the wrong things all along. Maybe Bitcoin’s greatest strength is in its functionality as a unit of account. After all, this is all that Bitcoin does. If you own 21 Bitcoin, you own one-millionth of the world's first absolutely scarce commodity. This might not make you rich overnight, but it just might have something to do with the opportunities available to your great-great-grandchildren.
Throughout history, whenever a prehistoric human tribe invented ceremonial burial, that tribe began to expand rapidly. Why? Because as soon as you invent belief in an afterlife, you also introduce the idea of self-sacrifice on a larger scale. People who held these beliefs were much easier for a despot to manipulate and send into battle with neighboring tribes. Religious leaders can use people’s fears and superstitions to have them commit all sorts of atrocities to their fellow man, and they still do so today. Belief in a “greater good” can be the most destructive idea that can pop up in a human mind. The Nazis of World War II Germany believed that exterminating Jews was for the “greater good” of their nation’s gene pool. Belief in noble causes often comes with unintended side effects, which can have disastrous consequences.
Religious leaders, political leaders, and other power-hungry sociopaths are responsible for the greatest crimes against humanity ever committed — namely, wars. Europeans often question the Second Amendment to the United States Constitution, which protects the right to bear arms, whenever a tragic school shooting occurs on the other side of the Atlantic. What everyone seems to forget is that less than a hundred years ago, Europe was at war with itself because its citizens had given too much power to their so-called leaders. The Nazis came to power in a democracy — never forget that. Our individual rights weren’t given to us by our leaders; we were born with them. Our leaders can’t give us anything; they can only force us to behave in certain ways. If we truly want to be in charge of our lives, we need to find the tools necessary to circumvent the bullshit ourselves.
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ e97aaffa:2ebd765d
2025-03-28 12:56:17
@ e97aaffa:2ebd765d
2025-03-28 12:56:17Nos últimos anos, tornei-me num acérrimo crítico do Euro, sobretudo da política monetária altamente expansionista realizada pelo Banco Central Europeu (BCE). Apesar de ser crítico, eu não desejo que Portugal volte a ter moeda própria.
No seguimento gráfico, é a variação do IPC de Portugal nos últimos 60 anos:
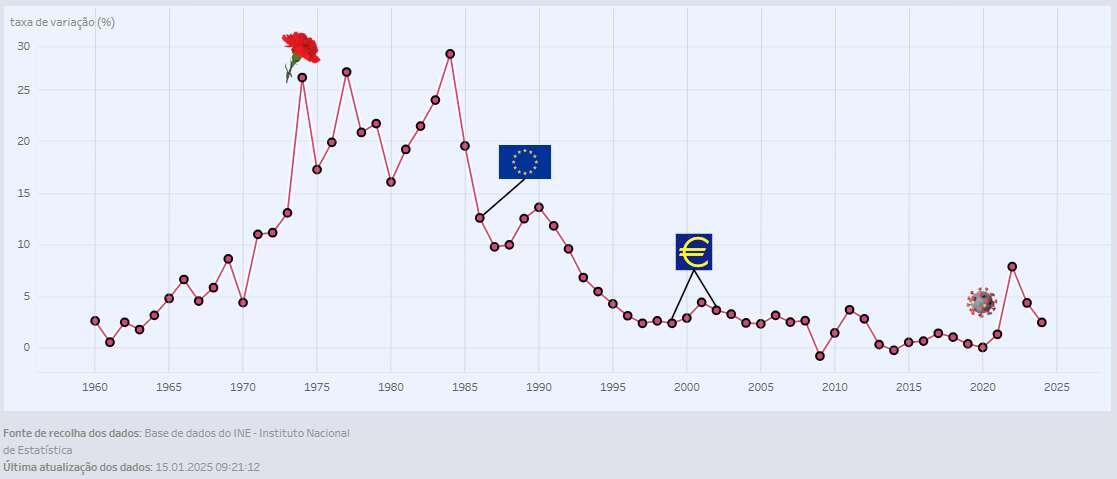
No gráfico inclui os momentos históricos, para uma melhor interpretação dos dados.
O Índice de Preços ao Consumidor (IPC) é usado para observar tendências de inflação. É calculado com base no preço médio necessário para comprar um conjunto de bens de consumo e serviços num país, comparando com períodos anteriores.
É uma ferramenta utilizada para calcular a perda de poder de compra, mas é uma métrica que é facilmente manipulada em prol dos interesses dos governos.
Análise histórica
No período marcelista, houve uma crescente inflação, devido a fatores, como os elevados custos da guerra e o fim dos acordos de Bretton Woods contribuíram para isso. Terminando com uma inflação superior a 13%.
Da Revolta dos Cravos (1974) até à adesão da CEE (atual União Europeia, UE), nos primeiros anos foram conturbados a nível político, mesmo após conquistar alguma estabilidade, em termos de política monetária foi um descalabro, com inflação entre 12% a 30% ao ano. Foi o pior momento na era moderna.
Com a entrada da CEE, Portugal ainda manteve a independência monetária, mas devido à entrada de muitos milhões de fundos europeus, essências para construir infraestrutura e desenvolver o país. Isto permitiu crescer e modernizar o país, gastando pouco dinheiro próprio, reduzindo a necessidade da expansão monetária e claro a inflação baixou.
Depois com a adesão ao Tratado de Maastricht, em 1991, onde estabeleceu as bases para a criação da União Económica e Monetária, que culminou na criação da moeda única europeia, o Euro. As bases eram bastante restritivas, os políticos portugueses foram obrigados a manter uma inflação baixa. Portugal perdeu a independência monetária em 1999, com a entrada em vigor da nova moeda, foi estabelecida a taxa de conversão entre escudos e euros, tendo o valor de 1 euro sido fixado em 200,482 escudos. A Euro entrou em vigor em 1999, mas o papel-moeda só entrou em circulação em 2002.
Assim, desde a criação até 2020, a inflação foi sempre abaixo de 5% ao ano, tendo um longo período abaixo dos 3%.
A chegada da pandemia, foi um descalabro no BCE, a expansão monetária foi exponencial, resultando numa forte subida no IPC, quase 8% em 2022, algo que não acontecia há 30 anos.
Conclusão
Apesar dos últimos anos, a política monetária do BCE tem sido péssima, mesmo assim continua a ser muito melhor, se esta fosse efetuada em exclusividade por portugueses, não tenho quaisquer dúvidas disso. O passado demonstra isso, se voltarmos a ser independentes monetariamente, será desastroso, vamos virar rapidamente, a Venezuela da Europa.
Até temos boas reservas de ouro, mas mesmo assim não são suficientes, mesmo que se inclua outros ativos para permitir a criação de uma moeda lastreada, ela apenas duraria até à primeira crise. É inevitável, somos um país demasiado socialista.
A solução não é voltar ao escudo, mas sim o BCE deixar de imprimir dinheiro, como se não houvesse amanhã ou então optar por uma moeda total livre, sem intromissão de políticos.
O BCE vai parar de expandir a moeda?
Claro que não, eles estão encurralados, a expansão monetária é a única solução para elevada dívida soberana dos estados. A única certeza que eu tenho, a expansão do BCE, será sempre inferior ao do Banco de Portugal, se este estivesse o botão da impressão à sua disposição. Por volta dos 5% é muito mau, mas voltar para a casa dos 15% seria péssimo, esse seria o nosso destino.
É muito triste ter esta conclusão, isto é demonstrativo da falta de competência dos políticos e governantes portugueses e o povo também tem uma certa culpa. Por serem poucos exigentes em relação à qualidade dos políticos que elegem e por acreditar que existem almoços grátis.
Bitcoin fixes this
-
 @ 57d1a264:69f1fee1
2025-03-28 10:32:15
@ 57d1a264:69f1fee1
2025-03-28 10:32:15Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.
The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous announcement.
Look forward for this to happen!
Spread the voice:
N: https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l... X: https://x.com/bitcoin_design/status/1905547407405768927
originally posted at https://stacker.news/items/927650
-
 @ 2b24a1fa:17750f64
2025-03-28 10:07:04
@ 2b24a1fa:17750f64
2025-03-28 10:07:04Der Deutsche Bundestag wurde neu gewählt. Für einige Abgeordnete und Regierungsmitglieder heißt es Time to Say Goodbye. Abschied ist ein scharfes Schwert.
https://soundcloud.com/radiomuenchen/nachruf-2-olaf-der-zeitenwender
Auch bei Radio München werden Trennungs- und Verlassenheitsgefühle getriggert. Umso mehr, wenn es sich nicht nur um duselige Allerweltsliebe handelt, sondern um den Abgang großer Helden. Sie bezahlten ihren todesmutigen und fast ehrenamtlichen Einsatz nicht mit dem Leben, jedoch mit der einen oder anderen Falte in Hemd oder Bluse, manchmal sogar im Gesicht. Was bleibt? Eine bescheidene Pension? Ein lausig bezahlter Manager-Job in einem Konzern? Wir wollen jedenfalls nicht, dass diese Volkshelden vom Zahn der Zeit abgenagt, vergessen werden und setzen ihnen deshalb ein bescheidenes akustisches, aber nachhaltiges Denkmal. Hören Sie die kleine satirische Reihe „Nachrufe“ von unserem Autor Jonny Rieder.\ Folge 2: Olaf der Zeitenwender
Sprecher: Karsten Troyke
Bild: Markus Mitterer für Radio München
Radio München\ www.radiomuenchen.net/\ @radiomuenchen\ www.facebook.com/radiomuenchen\ www.instagram.com/radio_muenchen/\ twitter.com/RadioMuenchen
Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS
-
 @ 2b24a1fa:17750f64
2025-03-28 10:03:58
@ 2b24a1fa:17750f64
2025-03-28 10:03:58Zwischen Überzeugungsarbeit und Propaganda verläuft ein schmaler Grad. Aber so oder so: Wer die subtileren Werkzeuge hat und vor allem die Mittel um Menschen zu kaufen, die diese dann anwenden, hat eindeutig die besseren Karten.
Dass die Bevölkerung nun wissen will, mit welchen Mitteln sie auf welche Weise beeinflusst werden soll, ist selbstverständlich. Wie nuanciert diese Beeinflussung stattfinden kann, darauf haben uns unsere Hörer beim letzten Beitrag von Milosz Matuschek: „Die ersten Köpfe rollen“ gestoßen. Es ging um die staatliche amerikanische Behörde für internationale Entwicklungshilfe USAID. Matuschek schrieb: „Man liest was von AID im Namen und denkt, was man denken soll: klingt nach Bob Geldof, barmherzigen Schwestern und “Brot für die Welt”.“ Man hatte das nicht nur optisch wahrgenommen, nein, diese Behörde wurde hierzulande, in allen Medien US AID genannt, was unsere Sprecherin Sabrina Khalil übernahm. Dass die United States Agency for International Development in USA so nicht gesprochen wird, schrieben uns gleich mehrere aufmerksame Hörer. Es ist sicherlich keine Paranoia darüber nachzudenken, ob die Bedeutung unserer Sprache, unserer Wörter bis hin zur Aussprache im Fokus der Manipulation steht. Dafür wird sehr viel Geld locker gemacht und unter anderem in die Medien gepumpt.
Hören Sie heute den zweiten Teil der Reihe „Die Corona-Connection“ mit dem Titel: „Der mediale Deep State wankt“. Sprecherin: Sabrina Khalil.
Das freie Medienprojekt Pareto kann übrigens Unterstützung gebrauchen, dafür wurde ein Crowdfunding auf Geyser gestartet, wo man mit Bitcoin/Lightning-Spenden helfen kann. Und für Spenden auf dem klassischen Weg finden Sie die entsprechende Bankverbindung auf der Homepage pareto.space/de.
Nachzulesen unter: www.freischwebende-intelligenz.org/p/unter…mediale
Foto: Gleichschaltung - sie melden exakt den gleichen Wortlaut.
-
 @ 7d33ba57:1b82db35
2025-03-28 09:13:56
@ 7d33ba57:1b82db35
2025-03-28 09:13:56Girona, one of Catalonia’s most charming cities, is a perfect mix of history, culture, and gastronomy. Famous for its well-preserved medieval old town, colorful houses along the Onyar River, and Game of Thrones filming locations, Girona is a must-visit destination in northern Spain.
🏰 Top Things to See & Do in Girona
1️⃣ Girona Cathedral (Catedral de Santa Maria) ⛪
- One of Spain’s most impressive cathedrals, with the widest Gothic nave in the world.
- Famous as the Great Sept of Baelor in Game of Thrones.
- Climb the steps for a breathtaking city view.
2️⃣ Walk the Medieval Walls (Passeig de la Muralla) 🏰
- Offers panoramic views of Girona and the surrounding countryside.
- A great way to see the city from above and explore its medieval history.
3️⃣ The Colorful Houses of the Onyar River 🌉
- Girona’s most iconic view, with brightly colored houses reflecting on the river.
- Best viewed from the Pont de les Peixateries Velles, designed by Gustave Eiffel.
4️⃣ Explore the Jewish Quarter (El Call) 🏡
- One of Europe’s best-preserved Jewish quarters, with narrow, medieval streets.
- Visit the Museum of Jewish History to learn about Girona’s Jewish heritage.
5️⃣ Arab Baths (Banys Àrabs) 🏛️
- A 12th-century Romanesque bathhouse, inspired by Moorish architecture.
- Features a beautiful central dome with columns.
6️⃣ Game of Thrones Filming Locations 🎬
- Walk in the footsteps of Arya Stark through the city’s winding streets.
- Visit the steps of the cathedral, the Jewish Quarter, and Arab Baths, all featured in the series.
7️⃣ Eat at a Michelin-Starred Restaurant 🍽️
- Girona is home to El Celler de Can Roca, a 3-Michelin-star restaurant, ranked among the best in the world.
- Try local Catalan dishes like "suquet de peix" (fish stew) and botifarra (Catalan sausage).
🚗 How to Get to Girona
✈️ By Air: Girona-Costa Brava Airport (GRO) is 20 min away, with budget flights from Europe.
🚆 By Train: High-speed AVE trains connect Barcelona (38 min), Madrid (3.5 hrs), and Paris (5.5 hrs).
🚘 By Car: 1 hr from Barcelona, 40 min from Figueres (Dalí Museum).
🚌 By Bus: Direct buses from Barcelona and the Costa Brava.💡 Tips for Visiting Girona
✅ Best time to visit? Spring & autumn (April–June & September–October) for pleasant weather. 🌤️
✅ Wear comfortable shoes – The old town is hilly with cobblestone streets. 👟
✅ Try xuixo – A delicious cream-filled pastry, unique to Girona. 🥐
✅ Visit early for Game of Thrones spots – They get crowded during the day! 🎥
✅ Take a day trip – Explore nearby Costa Brava beaches or Figueres (Dalí Museum). 🏖️ -
 @ 866e0139:6a9334e5
2025-03-24 10:51:52
@ 866e0139:6a9334e5
2025-03-24 10:51:52Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
Seit Sonntag (zu allem Glück auch noch meinem 45. Geburtstag) ist bei mir noch ein bisschen mehr los als sonst – und das liegt an Ihnen. Der Aufruf zur Gründung der „Friedenstaube“, einer unzensierbaren Friedenspublikation mit bekannten Stimmen aus der kritischen Szene, der Friedensbewegung und von Bürgerjournalisten ist bei Ihnen auf mehr als nur offene Ohren gestoßen! Ich bin regelrecht geplättet von den vielen Reaktionen, die ich noch gar nicht alle beantworten konnte.
Ich danke Ihnen herzlich für das Vertrauen in mich (auch wenn ich natürlich stark auf die Autoren angewiesen bin) und die überwältigenden Reaktionen: Es sind hunderte Abonnements für den Newsletter eingegangen, darunter einige bezahlte Abos und Förderabos und auch die ersten Genossenschaftsanteile wurden gezeichnet! Was mich besonders freut: Gut zehn weitere freiwillige Autoren wollen mitmachen und arbeiten bereits an den ersten Texten. Damit darf ich schon jetzt verkünden, dass die Genossenschaft definitiv gegründet werden kann, die Friedenstaube wird fliegen. Wie hoch und wie weit, das liegt dann nun nur noch in unser aller Hände.
Der Anfang ist jedenfalls gemacht. Die nächsten Wochen werden besonders arbeitsintensiv, ich bitte Sie um etwas Geduld: Aufbau einer Kernredaktion, Organisation der Abläufe, technologische Entwicklungsarbeiten, Genossenschaftsgründung etc. stehen jetzt auf der Agenda. Mit Tom-Oliver Regenauer darf ich den ersten Autor im redaktionellen Kernteam verkünden, der sich nicht nur große Verdienste im Schreiben erarbeitet hat (siehe u.a. sein Buch Hopium) sondern auch über Managementerfahrung verfügt; mit weiteren helfenden Händen bin ich im Gespräch.
Ich freue mich auf die (auch für mich) neue Erfahrung, quasi aus dem Nichts eine Publikation mit Redaktionsbetrieb und freien Autoren auf einer gänzlich neuen technologischen Infrastruktur aufzubauen. Es wäre illusorisch zu glauben, dass alles glatt gehen wird, denn wir starten quasi „on the go“, aber im Fall von Frieden oder Krieg gilt es, keine Zeit verstreichen zu lassen. Ich arbeite nach dem Motto „Tun, statt reden; zeigen, statt ankündigen; liefern, statt versprechen“.
Die ersten Texte zum Thema Frieden sind bereits publiziert, ein halbwegs geordneter Betrieb sollte ab April realistisch sein. Die Liste der Autoren wird regelmäßig aktualisiert, schauen Sie gerne hier (oder noch besser: hier) immer wieder herein. Dort finden Sie auch noch mal alle Infos, wenn Sie die Friedenstaube unterstützen wollen. Ab 1000 Euro/CHF werden Sie Genossenschafter, also Verleger!**
Auch an die bisherigen Unterstützer des Pareto-Projekts, der technologischen Basis der Friedenstaube, will ich hiermit schon etwas zurückgeben: Alle Spender für Pareto werden die Friedenstaube immer kostenlos lesen können. Sie, die Leser dieser Publikation haben die technologische Basis mit aufgebaut, die uns zur weltweit ersten, zensursicheren Friedenspublikation macht. Uns Autoren steht damit ein kompetentes Support-Team von inzwischen über zehn Entwicklern (und weiteren Helfern) an der Seite, welche die Friedenstaube am Fliegen halten werden.
Kontaktieren Sie mich gerne zu allen Fragen (je kürzer die Mail, desto früher kommt die Antwort): milosz\@pareto.space oder kontakt\@idw-europe.org
JETZT ABONNIEREN:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF/EURO werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie mich an: milosz@pareto.space oder kontakt@idw-europe.org.
Was bewegt mich beim Thema Krieg und Frieden?
Erlauben Sie mir einen kurzen persönlichen Prolog: Ich stamme aus Schlesien. Mein Urgroßvater kämpfte im I. Weltkrieg bei Verdun. Mein Großvater wurde in die Wehrmacht eingezogen, kämpfte im Partisanenkrieg in Jugoslawien, verlor Hand und Auge. Ein Bruder meiner Großmutter entzog sich und landete in Dachau. Ich kenne meine Familiengeschichte nur in groben Umrissen, vielen wird es ähnlich gehen. Einige meiner schlesischen Vorfahren waren später vor allem Lokführer. Aufgrund der bewegten schlesischen Geschichte wechselten sie mehrfach die Uniform. Die Tätigkeit und Fahrstrecke blieb die gleiche. Für wen oder was kämpften sie in Kriegen in welchen Uniformen? Vermutlich wussten sie es selbst nicht.
Auch ich könnte heute nicht genau sagen, welche Interessen und Mächte die Kriegsmaschinerie bedienen. Doch ich wüsste es gerne und Sie vielleicht auch. Kämpfen ohne letztlich zu wissen für wen und warum: Wozu? Krieg simuliert Sinn und Notwendigkeit und lässt einen am Ende mit den großen Fragen allein, ahnungslos gestorben im Schützengraben. Zivilisatorisch ist das ein Offenbarungseid.
Bin ich ein totaler Anti-Militarist? Ich glaube nicht. Ich habe nichts gegen die Idee privaten Waffenbesitzes. Ich kann der Idee der Landesverteidigung durchaus etwas abgewinnen. Den Wehrdienst habe ich bewusst nicht verweigert. Ich wollte die Erfahrung machen. Hier schreibt also auch ein Obergefreiter a. D. eines bayerischen Gebirgspionierbataillons bei Rosenheim mit bronzener Schützenschnur, der am MG durchaus treffsicher war. Aber eben auch jemand, den der Wehrdienst zum Teil-Pazifisten gemacht hat. Mir war nach dem Grundwehrdienst klar: Wir sind eine Gurkentruppe, reines Kanonenfutter. 20-jährige Grünschnäbel mit zu viel Testosteron und Hollywood in den Gliedern, aber wenig Ahnung.
Ich war also einer, der sich verlässlich mit anderen beim Orientierungslauf im Wald verirrte; einer, der mit anderen übermüdet beim ersten Wachdienst einpennte (und damit im Ernstfall den Tod im Schlaf kennengelernt hätte, denn just erfolgte ein simulierter „Angriff“); einer, der auch mal übernächtigt sein Gewehr vor dem Zelt vergaß (wir sollten dem G3 den Namen unserer damaligen Freundin geben – wie pervers – ich vergaß also „Petra“ vor dem Zelt) und schließlich einer, der die meiste Zeit des Dienstes fürs Vaterland letztlich mit dem Servieren von Getränken und Schinkennudeln im Offizierskasino verbrachte und die institutionalisierten Alkoholiker der Bundeswehr bei Laune hielt („it ain’t much, but it was honest work“).
Anders gesagt: Krieg – spätestens seitdem: ohne mich. Auch wenn ich gerne Ernst Jünger lese und zitiere (er war einfach ein großartiger Chronist und lebendiger Geist), seinen abenteuerlustigen Militarismus kreide ich ihm an und rufe ihm posthum hinterher: man muss nicht erst einen Sohn im Krieg verloren haben, um zum Pazifisten zu werden.
Weitere Störgefühle tauchten auf: In meiner Dissertation durfte ich mich u.a. mit philosophischen Theorien zum Gesellschaftsvertrag (u.a. Kant, Rousseau, Locke und Hobbes sind hier zu nennen) beschäftigen. Dies brachte mein Staatsverständnis gerade bei der Kriegsfrage noch mehr durcheinander. Wenn Mindestziel der Staatsgründung innere und äußere Sicherheit sind, aber letztlich nicht der Staat den Bürger, sondern der Bürger den Staat schützt, wozu sich dann eine Schutzmacht erfinden, die einen am Ende durch den Fleischwolf jagt? Hobbes setzte zumindest auf Söldner.
Kriege werden mit Lügen begonnen, wusste Julian Assange. Können Sie mit Wahrheit beendet oder gar verhindert werden? Seit Walter Lippmanns „Liberty and the News“ von 1920 weiß man spätestens, dass gesicherte Information im Krieg das seltenste Gut ist. Sagt Lippmann als oberster Mainstream-Journalist und Einflüsterer der Mächtigen. Jeder Journalist muss hier ein Störgefühl entwickeln, der Leser noch mehr. Der Journalist der Nachrichtenagentur ist selten im Geschehen sondern wird vom heimischen Militär gebrieft, sein Bericht landet dann in den Newstickern und Redaktionen. Die Kriegsmaschinerie produziert also auch ihre eigene Sicht auf die Dinge, die sie den Bürgern als die Realität verkauft.
Kein Wunder, dass jede abweichende Information massiv bekämpft werden muss. Im Krieg ist Zweifel gleich Verrat, quasi unsolidarisches Sektierertum und Wehrkraftzersetzung, wenn nicht Feindbegünstigung. Der kritische Journalist steht in Ausnahmezuständen, wie man schon bei Corona sehen konnte, automatisch aus Staatssicht im Lager des Feindes und wird entsprechend behandelt. Zensursicheres Publizieren ist dann nicht nur ein nettes feature, sondern notwendige Basisvoraussetzung. Vor kurzem war Twitter/X nicht mehr zugänglich wegen massiven Cyberattacken. Wenn dann noch Rundfunk und Presse auf der Propagandawelle surfen und die Plattformzensur wieder zuschlägt, wird das Angebot schnell dünn.
Wem aber dient Zensur und Propaganda? Die aktuelle Lage im Russland-Ukraine-Konflikt ist auch Gelegenheit, um zu zeigen: Es sind eben nicht nur staatliche Interessen, die hier verhandelt werden, sondern es muss (wieder mal) eine andere Entität mit am Tisch sitzen, man nenne sie Deep State oder wie auch immer. Europäische Eliten dienen offensichtlich Fremdinteressen, wenn sie mit Aufrüstungsplänen Volksvermögen verspekulieren oder darin (wie von der Leyen) ein notwendiges „Investment“ sehen. Von wem werden wir letztlich regiert? Auch diesem Themen-Komplex werde ich mich in der Friedenstaube nähern.
Es gibt viel zu tun, aber für mich ist klar: Frieden ist ohne Wahrheit nicht zu bekommen, deshalb ist Wahrheitssuche auch immer Friedenssuche, wie Wahrheitsliebe letztlich Friedensliebe ist.
Gerade fallen auch im Mainstream die Corona-Lügen zur Labortheorie in sich zusammen, fünf Jahre nach Ausrufung der Pandemie. Der Frieden hat nur eine Chance, wenn es uns gelingt, die Lügen nun möglichst synchron zu den Geschehnissen aufzudecken und zu dokumentieren.
Das ist mein persönlicher Wunsch, mit dem ich die Friedenstaube fliegen lasse.
Was ist Ihrer? Schreiben Sie es gerne in die Kommentare. Welche Erwartungen, Wünsche haben Sie an uns? Liebe Autoren: Was ist euer Beweggrund, für den Frieden zur Feder zu greifen?
Zeichnen Sie jetzt “Friedensanleihen”. Werden Sie Genossenschafter und Verleger der Friedenstaube ab 1000 Euro/CHF. Es können mehrere Anteile pro Person gezeichnet werden, es bleibt bei einem Stimmrecht pro Kopf. milosz\@pareto.space
P.S: Mit diesem Text testen wir die Newsletterfunktion erstmals an mehrere Hundert Mailadressen. Wenn Sie die Friedenstaube abonniert haben, sollten Sie diesen Artikel per Mail bekommen haben.
ANZEIGE:
Sie suchen nach dem einfachsten Weg, Bitcoin zu kaufen und selbst zu verwahren?* Die* Relai-App ist Europas erfolgreichste Bitcoin-App.* Hier kaufen Sie Bitcoin in wenigen Schritten und können auch Sparpläne einrichten. Niemand hat Zugriff auf Ihre Bitcoin, außer Sie selbst.* Relai senkt jetzt die Gebühr auf 1%, mit dem Referral-Code MILOSZ sparen Sie weitere 10%. (keine Finanzberatung). Disclaimer wg. EU-Mica-Regulierung: Die Dienste von Relai werden ausschließlich für Einwohner der Schweiz und Italiens empfohlen.
Join the marketplace of ideas! We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the Pareto Project? Zap me, if you want to contribute (all Zaps go to the project).
Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to team@pareto.space**
Not yet on Nostr and want the full experience? Easy onboarding via Start.
Pareto has started a crowdfunding campaign on Geyser. We were in the Top 3 in February, thank you for the support!
-
 @ 45c41f21:c5446b7a
2025-03-28 08:02:16
@ 45c41f21:c5446b7a
2025-03-28 08:02:16“区块链行业究竟是在做什么?”——这个问题我到现在还没有想得很清楚。谈论起来可以说很多东西,“确权”、“让每一个比特都有了稀缺性”、“数字黄金”、“点对点支付”,但是具体到了行业落地,又容易陷入“赌场”这个有点乌烟瘴气的现实。
但我想有一点是比较明确的,那就是区块链行业肯定是一个围绕资产的行业。这些资产又跟传统的资产很不一样,最简单的特征是它们都是一个个的代币,通过自动化和可验证的代码铸造、控制,我们可以统称为链上资产。从比特币、以太坊到现在,这中间不管过去了多少不同的周期和浪潮,核心不变的都是出现新一轮受追捧的资产。
既然区块链是关于链上资产的行业,那么最重要的是未来会出现什么新的资产,有什么样的新资产会上链。要回答这个问题,又要我们回过头去看看,从行业诞生至今,区块链留下了哪些有意义的、没意义的,有价值的、没价值的资产。
因此,有必要讨论一下链上资产的分类。
链上资产的种类很多,但总体上我觉得可以按满足需求的不同,做一些功能性的划分。同时,抛开去中心化、抗审查等等大词,链上资产与传统资产最重要的区别可以认为是安全性的来源。传统资产在传统的社会系统和金融系统中产生,而链上资产是通过可验证代码控制的,所以它的安全性的依赖很清晰,要比现实世界简单很多。
在不同的区块链系统中,使用不同的技术(比如POW/POS),设置不同的规则,拥有不同的治理机制,都会影响安全性。“安全性”和“满足什么样的需求”之间既不是正交的,也不是完全耦合的。在不同层级的安全性之下,可能都会出现满足某一类相同需求的产品,用户使用哪种产品,只取决于自己的风险偏好。另一方面,有些需求只可能在某些特定的安全性保障下才能得到满足,比如跨国际的全球化的抗通胀价值存储。
这篇文章只讨论一些比较简单的分类,可以假设在不同的安全性保障下,每个分类都有可能出现对应的产品。有些安全性是产品内生功能的一部分,有些则完全不影响。同时,这些分类也完全是主观的看法,不一定正确,我所希望的是引发更多对资产进行讨论。
核心资产(高安全性、强需求支撑)
- 比特币(BTC)
- 核心价值:全球化抗通胀、抗审查的“数字黄金”。
- 长期逻辑:全球法币超发背景下,BTC作为去中心化硬通货的需求不可替代。
这是整个行业最重要的资产。也是整个行业最核心的东西。在这个定位下,只会有一个赢者通吃。其他试图竞争的都很难生存下来。它对安全性的要求也是最高的。
经过验证的资产分类
这部分的资产可以认为是行业诞生至今,已经经过验证的、满足某真实需求、会长期存在的资产。
- 代表优质项目的资产(股票/ICO代币/治理代币等)
- 核心价值:类似于传统金融世界里的一级市场和二级市场。所谓的“优质”也不一定需要真实落地,可能是叙事/故事驱动,也可能有真实的现金流,但重要的是它能在市场上吸引人买卖。
- 关键指标:团队是否持续营销和建设?生态是否增长?项目是否解决实际问题?
- DeFi 资产
- 核心价值:链上金融系统的“基础设施工具”。
- 需求来源:对套利、链上资产理财的需求会永远存在。
- Meme币
- 核心价值:营销驱动+投机需求的结合体。
- 长期存在性:人性对暴富故事的追逐不会消失(如Pump.fun、SHIB)。
- 稳定币
- 核心价值:加密货币世界的“支付货币”。
- 需求刚性:交易媒介、避险工具、跨境支付(如USDT、USDC)。
在不同的安全性保障下,上面这些资产大部分都会有对应的产品。
比如稳定币在安全性上可以有中心化的 USDT ,也有去中心化的算法稳定币。理论上,安全性对稳定币是非常重要的。但现实中,“流动性”可能才是给用户传达“这东西到底安不安全“的产品特点,也是比较主要的竞争点。
Meme 则完全不需要安全性,所以对创业者来说在哪里做都差不多。哪里用户更多就适合去哪里。有时,安全性反而是它的阻碍。DeFi 的话,因人而异。安全性高低是否影响用户使用,完全取决于用户自己的风险偏好。
还未经过验证的资产(需求可能存在)
- NFT(收藏品)? 艺术、身份标识、游戏道具的数字化载体,但流动性差、炒作属性也不见得有 Meme 这么强。会长期存在吗?打个问号。
- DAO(准入/治理代币)? 去中心化组织的准入权/管理权通证,依赖 DAO 本身的价值和实际治理参与度决定的价值。DeFi DAO 可能是唯一一个有点发展的方向,其他还非常不成熟,有待验证。
- RWA(真实世界资产代币化)? 房产、债券等上链,需要解决法律合规与链下资产映射问题。不确定。
- 社交/游戏/内容资产 用户数据所有权货币化,还没有像样的有一些用户的产品,就更不用提形成规模经济了。
- AI 相关的资产? 是一个变数。如果未来会有成千上万的 AI 智能体与人类共存,链上是承载他们经济系统最合适的基础设施,这里会产生什么新的资产类型?值得期待。
这里面的资产类型,很多还没有找到真实的需求,至少没有经过验证。所以长期来看它们会是区块链行业的方向吗,需要打很多问号。既然需求本身没有得到验证,那么谈安全性对它们的影响,就更加无从谈起了。
当然,这里其实还有一个更有意思的部分,可以多聊一些。也就是共同知识(法律/合同/规则/代码)这一类资产。
在应用层,共同知识尚未有代币化的尝试,也难以对其具体价值做定量分析。但如果要说有的实践,以太坊通过交易收取 gas 费和 CKB 通过 Cell 存储状态收取“押金”算是一种在底层的 generalize 的尝试。这种尝试是定量的,可验证的。
以太坊的问题是经济模型不 make sense 导致状态爆炸,ckb 相比是更简单、更明确的。但这里的问题变成了,公链需要通过区块空间的竞争来展示这一种需求是否真的成立。区块空间越紧张,需求就越大。同时安全性越高,对共同知识的保障就越强,也会体现区块空间的价值。
但另一方面,是否有开发者在上面开发应用,会更大的影响这一点。因此开发工具、开发者生态在现阶段可能更重要。
最后
写到这里,发现很多资产似乎又是老生常谈。但从满足需求和安全性两个角度来思考,算是追本溯源的尝试。现在我们面临的处境是,问题还是老的问题,答案是否有新的答案,期待更多讨论。
- 比特币(BTC)
-
 @ a60e79e0:1e0e6813
2025-03-23 16:10:10
@ a60e79e0:1e0e6813
2025-03-23 16:10:10**This is a long form note test of a post that lives on my Nostr educational website Hello Nostr **
In early 2025, social media is the most common use case for Nostr (and probably the reason you're reading this). Nostr is SO much more than just social media, but that's where the bulk of the activity is, and is what I'm focusing on in this post. Even though the protocol is still so young, that has not prevented an explosion of excellent social media focused clients that predominantly coalesce around the Twitter (X) style feed, containing shorter form content, often with images, and the ability to comment, like and share.
This first steps guide showcases one of the most polished and simplest examples of such a client, Primal. Primal is a cross platform app, that also works on your computer too. The steps that follow are demonstrated on iPhone, but should be identical for Android users. There may be some topics of concepts here that are new to you, to learn more about them, check out our Nostr 101 to learn more about Nostr basics and why it matters.
You can and should explore all of the other options available to you, that's the beauty of Nostr, you're free to choose how and where to interact with your social network. No lock in. No walled gardens. True freedom.
Getting Started
-
Go to your app store and download Primal to your Android or iPhone
-
Open Primal and choose Create Account. Choose your public display name and add a short bio about yourself.

- Select your chosen interests from the list provided. This will bootstrap your feed and auto-follow a number of accounts so that your feed is not completely empty when starting out.
- Review your account info and tap Create Account Now. Take note of the fact that 'Your Nostr Key is available in your Account Settings'. We'll revisit this shortly.

- Next is an optional step of activating the wallet feature within Primal. Having a wallet within your social client enables you to send and receive value (known as 'Zaps') in the form of Bitcoin. On Facebook and Twitter you can like a post, but it means much more to send someone fractions of a penny (or more if you like) to show your appreciation for their insights. You'll need to provide some personal information to enable the wallet, including an email address.
Using the internal wallet and purchasing sats with your credit card will tie your Nostr identity to your real ID. Think very carefully before carrying out this step.
Learn more in the detailed section at the end of this post.
- That's it, you're now set up and ready to start sharing your thoughts, feelings and memes with the world via a decentralized and censorship resistant social network. To post your first note and say hello to the Nostr world, tap the + in the bottom right corner.
- If you activated the wallet at step 5, you might want to deposit some Bitcoin in there to allow you to send some value to your friends. There are three main ways to do this:
- Post some awesome content and have people send you value in the form of 'Zaps'
- Send some Bitcoin from a wallet you already have
- Purchase some directly within Primal
The latter is made very simple thanks to the in-app purchase feature, which allows you to purchase a small amount with the card you likely already have connected to your Apple/Google account. All you need to do is tap 'Buy Sats Now'.
- Next, let's look at the different feeds available on our home screen. Tap 'Latest' at the top of the screen and you can toggle between three different types of home feeds, great for discovering new people and content.
- Let's assume you already have some friends on Nostr and want to find and follow them. Tap the search icon in the top right corner, the enter the name of the person you want to follow. Once on their profile, simply tap the 'Follow' button.
- So you found a friend and want to start interacting with them so they know you made it over to Nostr. Simply find a note you like and choose from the different types of interactions available. From left to right they are:
- Comment
- Zap (send value from your wallet to theirs)
- Like
- Repost
- Bookmark

When Zapping, a single tap will send a tiny amount of 42 sats. If you want to send more, or a custom amount, tap and hold the zap button to bring up a selector menu. All default zap amounts are configurable in the app settings page.
- After you've started posting and interacting with others, you'll likely receive some notifications to tell you. Notifications can be filtered into interaction types.
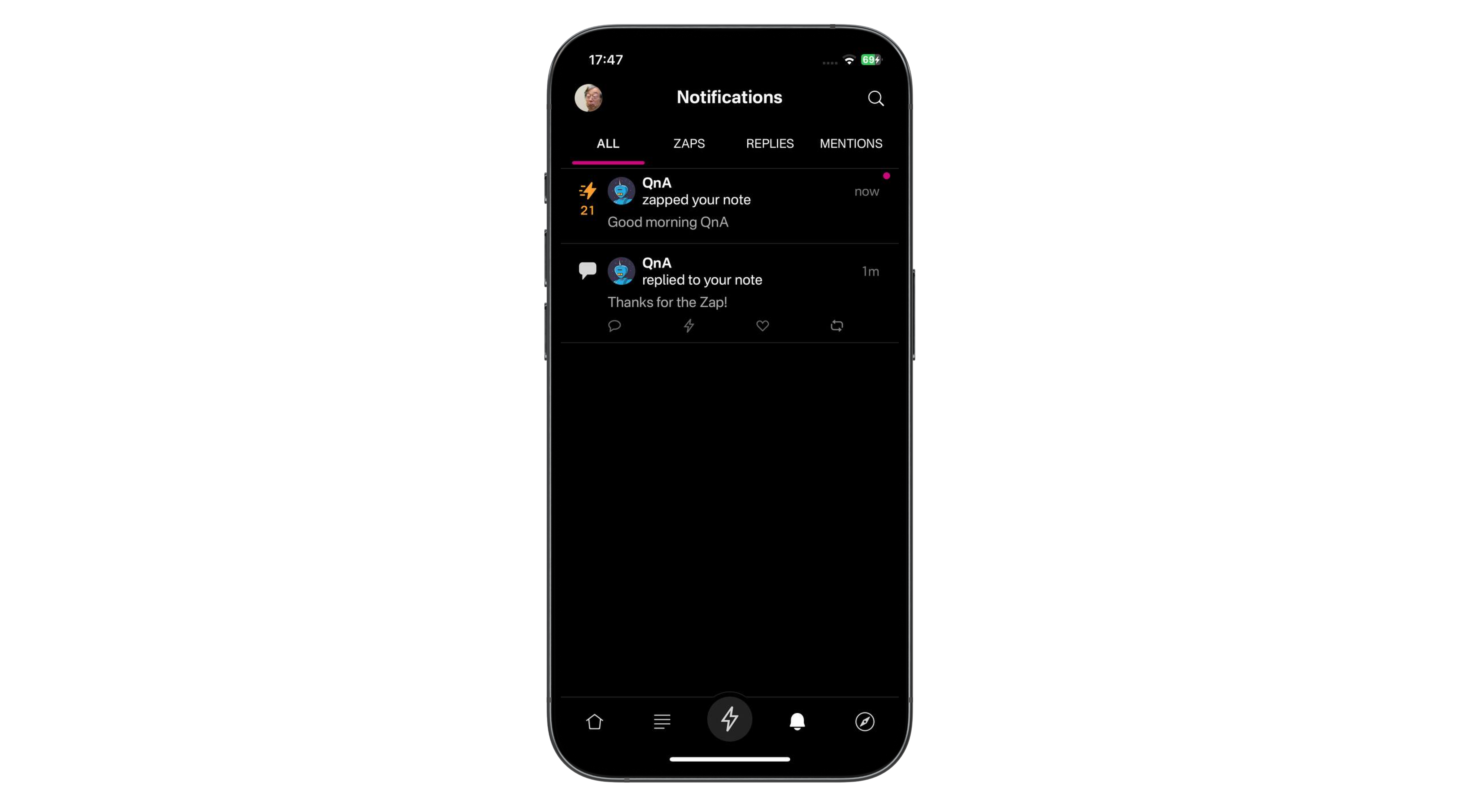
- Another great way to find more people to follow and interact with is to use the discover page. To open it, tap the compass in the bottom right corner of the screen. Here you'll be able to browse different types of pre-built feeds, trending profiles, notes with large zaps and extra topics.

The Important Part
You might have noticed that throughout that setup, you were not asked for a unique username, nor were you asked for a password. So how the hell is this secure? What happens if you log out? Is your account lost forever?
This is where Nostr really starts to shine. Just like in Bitcoin or other cryptocurrencies, your Nostr account is protected by a 'Private Key'. Anyone with knowledge of the private key can access your account in any Nostr client. No private key, no access. So let's make sure you have a backup copy of it, so you can still recover access to your account in the event you lose your phone!
Tap on your profile image in the top left of the screen. Then tap Settings > Keys. Here you'll see two keys, one public and one private. Your public key is how people find you on Nostr. It is often referred to by its more technical name 'nPub' which is the prefix if the key itself. Your public key is designed to be exactly that, public!
Your private key is sometimes referred to by its technical name 'nSec' which is also the prefix of the key. Copy your private key and paste it somewhere safe and secure, in a location accessible independently from your phone, and only by you.
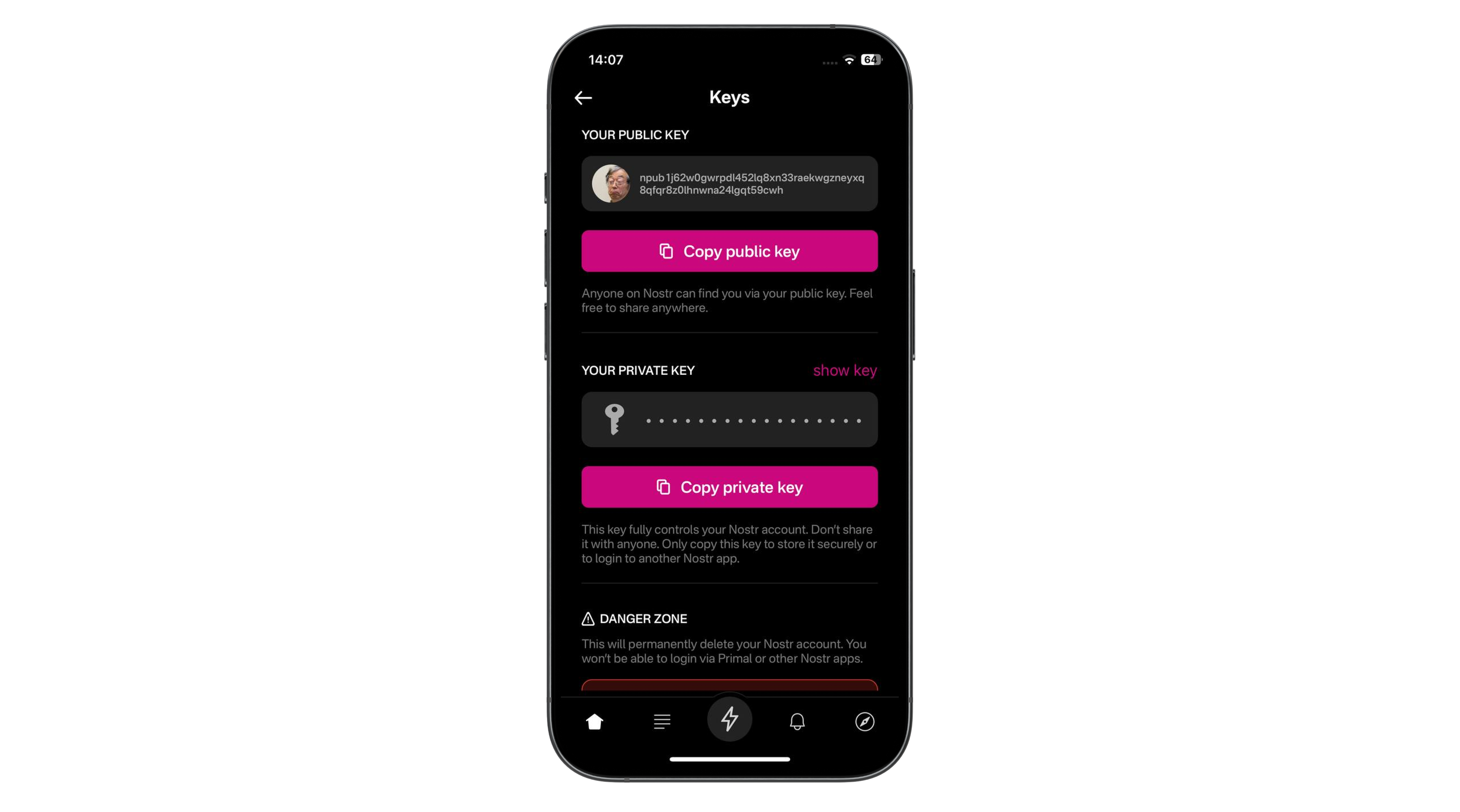
If you were to lose your phone, or accidentally delete the Primal app, now all you'd need to do is head back to step 1 above and choose Sign In. You'd then be asked to paste your private key, after which your profile and content would be magically restored.
Your private key can be imported into any other Nostr social client for the same result.
Things to Consider
This post has one primary focus - To get you from zero to posting and zapping in the quickest time and with the least friction. To achieve this, there are some trade-offs made that you should be aware of.
Custodial Wallet
The built in wallet is a custodial one. This means that the funds within are ultimately controlled by the developers behind Primal. They may be good actors, but you should approach the amount of money you maintain inside this wallet accordingly. If your wallet balance ever gets to a balance that makes you uncomfortable, you should send a good chunk of it out to another Bitcoin wallet where you control the keys. I recommend Phoenix or Zeus.
Those sats are never truly yours until you withdraw them to a self-custodial wallet
Wallet Privacy
If you choose to top up the wallet using the convenient in-app purchase method, you will tie that small amount of Bitcoin ownership to your Nostr account. If you Nostr account is literally your name, you might not have an issue with this, but often times people like to remain pseudonymous online. If you fall into that category, using your credit card to deposit Bitcoin into your Nostr account is not a good idea.
Android users of Primal can use an advanced technology called Nostr Wallet Connect (NWC) to connect an external Lightning wallet to their Nostr account in Primal. We'll cover this in a subsequent post.
Your private key allows you to take your profile and social network to any other client
If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I'll be sure to Zap you back! ⚡️
-
-
 @ c631e267:c2b78d3e
2025-03-21 19:41:50
@ c631e267:c2b78d3e
2025-03-21 19:41:50Wir werden nicht zulassen, dass technisch manches möglich ist, \ aber der Staat es nicht nutzt. \ Angela Merkel
Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach. Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides.
Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar, dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.

Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen, die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch.
Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war vielleicht früher einmal so, heute ist eher das Gegenteil gemeint.
In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien beleuchtet. Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als «Technofeudalismus» angeprangert.
Nationale Zugangspunkte für Mobilitätsdaten im Sinne der EU gibt es nicht nur in allen Mitgliedsländern, sondern auch in der Schweiz und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen Identifizierungssystem für «nachhaltigen Verkehr und Tourismus».
Natürlich marschiert auch Deutschland stracks und euphorisch in Richtung digitaler Zukunft. Ohne vernetzte Mobilität und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität voll auf Digitalisierung».
Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten, das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Er ist zuerst auf Transition News erschienen.
-
 @ 05cdefcd:550cc264
2025-03-28 08:00:15
@ 05cdefcd:550cc264
2025-03-28 08:00:15The crypto world is full of buzzwords. One that I keep on hearing: “Bitcoin is its own asset class”.
While I have always been sympathetic to that view, I’ve always failed to understand the true meaning behind that statement.
Although I consider Bitcoin to be the prime innovation within the digital asset sector, my primary response has always been: How can bitcoin (BTC), a single asset, represent an entire asset class? Isn’t it Bitcoin and other digital assets that make up an asset class called crypto?
Well, I increasingly believe that most of crypto is just noise. Sure, it’s volatile noise that is predominately interesting for very sophisticated hedge funds, market makers or prop traders that are sophisticated enough to extract alpha – but it’s noise nonetheless and has no part to play in a long-term only portfolio of private retail investors (of which most of us are).
 Over multiple market cycles, nearly all altcoins underperform Bitcoin when measured in BTC terms. Source: Tradingview
Over multiple market cycles, nearly all altcoins underperform Bitcoin when measured in BTC terms. Source: TradingviewAha-Moment: Bitcoin keeps on giving
Still, how can Bitcoin, as a standalone asset, make up an entire asset class? The “aha-moment” to answer this question recently came to me in a Less Noise More Signal interview I did with James Van Straten, senior analyst at Coindesk.
Let me paraphrase him here: “You can’t simply recreate the same ETF as BlackRock. To succeed in the Bitcoin space, new and innovative approaches are needed. This is where understanding Bitcoin not just as a single asset, but as an entire asset class, becomes essential. There are countless ways to build upon Bitcoin’s foundation—varied iterations that go beyond just holding the asset. This is precisely where the emergence of the Bitcoin-linked stock market is taking shape—and it's already underway.”
And this is actually coming to fruition as we speak. Just in the last few days, we saw several products launch in that regard.
Obviously, MicroStrategy (now Strategy) is the pioneer of this. The company now owns 506,137 BTC, and while they’ll keep on buying more, they have also inspired many other companies to follow suit.
In fact, there are now already over 70 companies that have adopted Strategy’s Bitcoin playbook. One of the latest companies to buy Bitcoin for their corporate treasury is Rumble. The YouTube competitor just announced their first Bitcoin purchase for $17 million.
Also, the gaming zombie company GameStop just announced to raise money to buy BTC for their corporate treasury.
 Gamestop to make BTC their hurdle rate. Source: X
Gamestop to make BTC their hurdle rate. Source: XETF on Bitcoin companies
Given this proliferation of Bitcoin Treasury companies, it was only a matter of time before a financial product tracking these would emerge.
The popular crypto index fund provider Bitwise Investments has just launched this very product called the Bitwise Bitcoin Standard Corporations ETF (OWNB).
The ETF tracks Bitcoin Treasury companies with over 1,000 BTC on their balance sheet. These companies invest in Bitcoin as a strategic reserve asset to protect the $5 trillion in low-yield cash that companies in the US commonly sit on.
 These are the top 10 holdings of OWNB. Source: Ownbetf
These are the top 10 holdings of OWNB. Source: OwnbetfETF on Bitcoin companies’ convertible bonds
Another instrument that fits seamlessly into the range of Bitcoin-linked stock market products is the REX Bitcoin Corporate Treasury Convertible Bond ETF (BMAX). The ETF provides exposure to the many different convertible bonds issued by companies that are actively moving onto a Bitcoin standard.
Convertible bonds are a valuable financing tool for companies looking to raise capital for Bitcoin purchases. Their strong demand is driven by the unique combination of equity-like upside and debt-like downside protection they offer.
For example, MicroStrategy's convertible bonds, in particular, have shown exceptional performance. For instance, MicroStrategy's 2031 bonds has shown a price rise of 101% over a one-year period, vastly outperforming MicroStrategy share (at 53%), Bitcoin (at 25%) and the ICE BofA U.S. Convertible Index (at 10%). The latter is the benchmark index for convertible bond funds, tracking the performance of U.S. dollar-denominated convertible securities in the U.S. market.
 The chart shows a comparison of ICE BofA U.S. Convertible Index, the Bloomberg Bitcoin index (BTC price), MicroStrategy share (MSTR), and MicroStrategy bond (0.875%, March 15 203). The convertible bond has been outperforming massively. Source: Bloomberg
The chart shows a comparison of ICE BofA U.S. Convertible Index, the Bloomberg Bitcoin index (BTC price), MicroStrategy share (MSTR), and MicroStrategy bond (0.875%, March 15 203). The convertible bond has been outperforming massively. Source: BloombergWhile the BMAX ETF faces challenges such as double taxation, which significantly reduces investor returns (explained in more detail here), it is likely that future products will emerge that address and improve upon these issues.
Bitcoin yield products
The demand for a yield on Bitcoin has increased tremendously. Consequently, respective products have emerged.
Bitcoin yield products aim to generate alpha by capitalizing on volatility, market inefficiencies, and fragmentation within cryptocurrency markets. The objective is to achieve uncorrelated returns denominated in Bitcoin (BTC), with attractive risk-adjusted performance. Returns are derived exclusively from asset selection and trading strategies, eliminating reliance on directional market moves.
Key strategies employed by these funds include:
- Statistical Arbitrage: Exploits short-term pricing discrepancies between closely related financial instruments—for instance, between Bitcoin and traditional assets, or Bitcoin and other digital assets. Traders utilize statistical models and historical price relationships to identify temporary inefficiencies.
- Futures Basis Arbitrage: Captures profits from differences between the spot price of Bitcoin and its futures contracts. Traders simultaneously buy or sell Bitcoin on spot markets and enter opposite positions in futures markets, benefiting as the prices converge.
- Funding Arbitrage: Generates returns by taking advantage of variations in Bitcoin funding rates across different markets or exchanges. Funding rates are periodic payments exchanged between long and short positions in perpetual futures contracts, allowing traders to profit from discrepancies without significant directional exposure.
- Volatility/Option Arbitrage: Seeks profits from differences between implied volatility (reflected in Bitcoin options prices) and expected realized volatility. Traders identify mispriced volatility in options related to Bitcoin or Bitcoin-linked equities, such as MSTR, and position accordingly to benefit from volatility normalization.
- Market Making: Involves continuously providing liquidity by simultaneously quoting bid (buy) and ask (sell) prices for Bitcoin. Market makers profit primarily through capturing the spread between these prices, thereby enhancing market efficiency and earning consistent returns.
- Liquidity Provision in DeFi Markets: Consists of depositing Bitcoin (usually as Wrapped BTC) into decentralized finance (DeFi) liquidity pools such as those on Uniswap, Curve, or Balancer. Liquidity providers earn fees paid by traders who execute swaps within these decentralized exchanges, creating steady yield opportunities.
Notable products currently available in this segment include the Syz Capital BTC Alpha Fund offered by Syz Capital and the Forteus Crypto Alpha Fund by Forteus.
BTC-denominated share class
A Bitcoin-denominated share class refers to a specialized investment fund category in which share values, subscriptions (fund deposits), redemptions (fund withdrawals), and performance metrics are expressed entirely in Bitcoin (BTC), rather than in traditional fiat currencies such as USD or EUR.
Increasingly, both individual investors and institutions are adopting Bitcoin as their preferred benchmark—or "Bitcoin hurdle rate"—meaning that investment performance is evaluated directly against Bitcoin’s own price movements.
These Bitcoin-denominated share classes are designed specifically for investors seeking to preserve and grow their wealth in Bitcoin terms, rather than conventional fiat currencies. As a result, investors reduce their exposure to fiat-related risks. Furthermore, if Bitcoin outperforms fiat currencies, investors holding BTC-denominated shares will experience enhanced returns relative to traditional fiat-denominated investment classes.
X: https://x.com/pahueg
Podcast: https://www.youtube.com/@lessnoisemoresignalpodcast
Book: https://academy.saifedean.com/product/the-bitcoin-enlightenment-hardcover/
-
 @ 1c19eb1a:e22fb0bc
2025-03-21 15:48:32
@ 1c19eb1a:e22fb0bc
2025-03-21 15:48:32For our first edition of #Nostrversity, we'll be diving into Nostr Wallet Connect, or #NWC; a handy means of connecting a #Lightning wallet to your favorite #Nostr app that quickly became the standard and is now an essential part of onboarding to Nostr for any new user who wants to experience the magic of zaps. Yet NWC enables so much more than just one-tap-zapping, as we will see when we look a little closer at how it works under the hood.
Lightning History on Nostr
Back in the wild-west days of Nostr, before nostr:npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s invented zaps, Bitcoin psychopaths were already sending sats to one another over Nostr. However, the way we had to do it back then was by going into our Lightning wallet, selecting "receive," inputting an amount we wanted, and copy/pasting an invoice from the wallet into our Nostr note, then hope someone was willing to pay it. And the payment side was just as cumbersome, requiring manually copying the invoice from your Nostr client, pasting it into a Lightning wallet so you could see how much the other user wanted, and then deciding if you were even willing to send it.
It didn't take long before Nostr clients, particularly on mobile, started rendering Lightning invoices in a convenient format that showed the invoice amount and a "Pay" button, that would prompt the user to open a Lightning wallet. This took out a decent amount of friction for the sender, but it was still just as big a hassle for the receiver.
Then zaps came along, and soon everyone had the ability to send sats to any other user when they found value in the content they posted. At least, any other user that added their Lightning address to their profile and whose Lightning wallet provider supported sending a "paid" receipt to a Nostr relay. Receiver friction had been virtually eliminated and the sats began to flow. Nostr also became the de facto directory for Bitcoiner payment addresses. If you heard nostr:npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83a say something brilliant on a podcast, you could just look her up on any Nostr client with zaps and send some sats her way as a thank you.
Enter the zapathon, a community event with one purpose: break nostr:npub1hcwcj72tlyk7thtyc8nq763vwrq5p2avnyeyrrlwxrzuvdl7j3usj4h9rq by zapping each other so much it was effectively a DDOS attack. Sure, it was a stress test on other wallets too, but most users were on Wallet of Satoshi because it was the easiest way to get a Lightning address with a mobile wallet.
It was a ton of fun flinging sats around as fast as your fingers would let you! However, a new friction point was soon discovered from trying to zap so frequently. Every time you tapped the zap icon in your Nostr client, you had to wait for your wallet to open and present the invoice to approve payment, then switch back to your Nostr client to zap the next note. Not a big deal when you only send a zap occasionally, but when trying to zap every note in your feed, it adds a significant amount of time and extra clicks. In fact, this small amount of friction, whether you realize it or not, often acts as just enough of a barrier to zapping that you will choose not to zap a post you found some value in, just because of the extra 5 seconds it takes to load into your wallet app, approve the payment, and switch back to your Nostr client.
Wouldn't it be amazing if we could have one-tap-zaps?
I can't recall if there were any other methods by which this was achieved, but the method that caught on was developed and released into the wild by nostr:npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm, who called it Nostr Wallet Connect. At that time (March of 2023), Alby was a custodial Lightning wallet for your web browser, and while you could connect your own node to it using LNDHub, most people just stuck with their custodial option since it came with a Lightning address. Nostr Wallet Connect was, at that time, a way to connect your Alby wallet to a Nostr client.
I am not certain which client was the first to support NWC, but I know that #Amethyst was pretty early on, and it was an instant success. Users could get a "connection string" from Alby, paste it into Amethyst, and zap with a single tap of their finger. Just like zaps themselves had eliminated the friction for receiving payments via Lightning for anyone with a Lightning address, Nostr Wallet Connect had eliminated the friction for sending payments. No more wasted seconds switching back and forth between Nostr client and wallet app, just tap and zap sent, tap again and another zap gone.
Of course, this meant that it was all too easy to send way more sats out of your wallet than you intended. This was solved by the ability to set budgets, so your wallet would cut you off once you reached the max amount you had set for yourself.
Because Alby had made Nostr Wallet Connect open source and part of the Nostr protocol, it didn't take long before more and more clients started adding support for it. Users demanded it and wouldn't shut up about it until it was added. Other wallet providers also saw the value of including it. Now it is simply expected, and any wallet that doesn't include it won't attract Nostr users.
Notably, Wallet of Satoshi went from being the most popular wallet among Nostr users to being a rare and quaint throwback to a bygone era, because they never integrated NWC and they pulled away from serving anyone in the U.S. out of fear of regulation under the Biden administration.
So we arrive at the state of Lightning on Nostr today, with Lightning addresses in our profiles for receiving zaps, and Nostr Wallet Connect for sending, and hard pressed to find Nostr clients that don't support both.
So... How does it work?
All of that history is great, but you're here to learn how this technology works. What is happening behind the scenes when you tap that little ⚡️ icon and sats seem to magically leave your Lightning wallet and show up on your screen as a zap underneath the latest nostr:npub1lrnvvs6z78s9yjqxxr38uyqkmn34lsaxznnqgd877j4z2qej3j5s09qnw5 meme, without you having to fiddle around with any Lightning invoices at all?
It's really quite simple, in the end. Your wallet communicating with your Nostr client using a Nostr relay in the middle, the same way you communicate with other Nostr users by saving notes to a relay that they can retrieve them from.
First, your Nostr client has to know how to "tag" your wallet, and on which relay to send it notes. This is why you need to get a "connection string" from your wallet to paste into your Nostr client. This string has all the information that is needed for your Nostr client to know how to communicate with your wallet, and for your wallet to be sure that the payment requests are authorized by you.
Let's take a look at an example connection string:
nostr+walletconnect://b889ff5b1513b641e2a139f661a661364979c5beee91842f8f0ef42ab558e9d4?relay=wss%3A%2F%2Frelay.damus.io&secret=71a8c14c1407c113601079c4302dab36460f0ccd0ad506f1f2dc73b5100e4f3cLooks like a bunch of gobbledygook, right? We'll break down each of its parts and see what it does.
nostr+walletconnect://This portion just defines the type of information that follows it. Because the string starts with this marker, any software reading it will know that what follows is information on how to communicate with a Lightning wallet, so long as it has been programmed to recognize it.
b889ff5b1513b641e2a139f661a661364979c5beee91842f8f0ef42ab558e9d4This section is just a public key, the same as an npub. In fact, it can be readily converted to an npub if you want using nostr:npub1zdr58j526qsrkdjhcg9xs60xfutqeey2ucugms04efnlx3spnmns2eqha9's key converter. It's a nostr identity just like yours or mine, but you won't find any GM posts or catstr pictures in its note history. It's only posting special note types used by NWC. This public key belongs to your Lightning wallet, and just like you can have multiple npubs for each of your alter egos, your wallet creates a separate public key to use with each new app you want to connect it to. Or at least it should. The Nostr client you use will tag your wallet in notes it creates by using this public key.
relay=wss%3A%2F%2Frelay.damus.ioThis section is probably easily recognizable. It's the same as typing
relay=wss://relay.damus.io, except that it has to use%3A%2F%2Fin place of://. This tells your Nostr client which relay it needs to use to communicate with your wallet. Hopefully your wallet uses a relay with high up-time, because one of the major ways for NWC to fail is if the relay is down. You also can't use just any relay. It has to accept the note kinds used by NWC, which is why wallets don't typically let their users choose the relay that will be used. You also can't just modify the connection string to use a relay you prefer, even if you know it allows NWC note kinds. This is because it will result in your Nostr client sending requests to your wallet on that relay, but your wallet is not reading from that relay, so it will never receive the requests.secret=71a8c14c1407c113601079c4302dab36460f0ccd0ad506f1f2dc73b5100e4f3cThis is just a Nostr private key. It's an nsec, but in hex format. Your wallet is giving your Nostr client a private key that it must use to sign all of the requests it sends to your wallet. No request signed by any other private key will be answered by your wallet. Your wallet will generate a separate private key for each connection string, allowing you as the user to revoke those connections individually, or set a separate budget for each connection.
When you tap the ⚡️ icon in your Nostr client, it obtains a Lightning invoice from the user's wallet you are trying to zap using their Lightning address. It then creates a note tagging your wallet's public key and requesting payment of that Lightning invoice, signing the note with the private key your wallet generated for it, and writing that note to the specified Nostr relay. Your wallet is constantly checking that relay for new notes and when it sees the payment request signed by an authorized private key, it pays the invoice, so long as it is within the budget you set, and sends out a payment receipt stating it has been paid so your client can light up the zap indicator to show that it was successful. All of this from a single tap of your finger in Amethyst.
More than Zaps
Now that we know the basics of how NWC works, it doesn't take much extrapolation to realize that this communication between wallet and Nostr client could be used for much more than just payment requests. A client could ask for your wallet's balance information, or transaction history, or ask for a lightning invoice. In fact, why does it have to be a Nostr client making those requests at all? Why not a mobile wallet app, or browser extension?
One of the major pieces of friction felt by those who run Lightning nodes is the difficulty of connecting to them remotely in a secure way. nostr:npub1aghreq2dpz3h3799hrawev5gf5zc2kt4ch9ykhp9utt0jd3gdu2qtlmhct and nostr:npub126ntw5mnermmj0znhjhgdk8lh2af72sm8qfzq48umdlnhaj9kuns3le9ll allow for connecting via Tor by default, but that can be painfully slow and unreliable. Anyone who has set up a connection to their node via LND Rest over Tor to their nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5 wallet can attest to the frustration of opening their wallet and waiting several seconds for the interface to load, only to receive a timeout notice.
Nostr Wallet Connect has eliminated this issue thanks to Alby Hub and Alby Go. Just create a new connection in Alby Hub, give it a budget, and scan the QR code with Alby Go and you have a fully-functional, mobile Lightning wallet connected to your node at home that loads extremely quickly and reliably, so long as the Nostr relay in-between is up and running.
Now, you may be concerned that the information being passed back and forth on this Nostr relay is incredibly sensitive financial information, especially if balance and transaction history is involved. However, this is not a concern because the content of the notes is fully encrypted. The relay owner, or anyone else with access to read data on that relay, has no idea what information is contained in the messages being sent between wallet provider and Nostr client, or Lightning node and mobile wallet. And because neither npub being used by your wallet provider or your Nostr client is the same as your npub, there is nothing tying the messages to you.
As a result, NWC is quickly becoming an integral piece of Lightning infrastructure, even if those making use of it have no interest in joining Nostr at all.
The Future of NWC
To wrap this up, I'd like to point the reader to recent developments with Nostr Wallet Connect, and other use-cases we could very well see in the near future.
First, NWC may not just be for Lightning. nostr:npub1utx00neqgqln72j22kej3ux7803c2k986henvvha4thuwfkper4s7r50e8 recently revealed that he has a working prototype of on-chain payments via NWC.
nostr:nevent1qvzqqqqqqypzpckv7l8jqspl8u4y54dn9rcduwlrs4v2040nxce0m2h0cunvrj8tqyw8wumn8ghj7un9d3shjtnzd96xxmmfdecxzunt9e3k7mf0qyfhwumn8ghj7am0wsh82arcduhx7mn99uq32amnwvaz7tmjv4kxz7fww468smewdahx2tcqyzswntflhlvuea2uf3035r94azm32frnskk5qp2evj43x6nz6kt9zd7j485
We are already seeing it used with eCash wallets like nostr:npub1kvaln6tm0re4d99q9e4ma788wpvnw0jzkz595cljtfgwhldd75xsj9tkzv. There is no reason we shouldn't expect to see it used with all forms of Bitcoin payments. This could lead to an explosion of available wallet applications for all platforms, since they will simply be an interface for communicating with your node or wallet provider.
NWC can also be used for subscriptions, as alluded to in nostr:npub1utx00neqgqln72j22kej3ux7803c2k986henvvha4thuwfkper4s7r50e8's note above. Before you protest about what an awful monetization model subscriptions are, I generally agree. That said, subscriptions where the user remains in control the entire time, and can unilaterally cancel the subscription at any time, without having to jump through hoops and give explanations about why they no longer want to use the service, is a massive improvement over the current status quo. Remember, NWC allows the user to set a budget for each connection. This means your subscription can't incrementally increase its monthly fee on you. Not without you willingly going into your wallet settings and adjusting the monthly budget, at any rate.
Last one before we close this out: NWC can be used for streaming services where you pay only for what you use, and give yourself a budget. Instead of paying a monthly subscription to Netflix, you could pay per minute that you watch. Previously this could only be done by topping up a wallet controlled by the service itself, the way nostr:npub1v5ufyh4lkeslgxxcclg8f0hzazhaw7rsrhvfquxzm2fk64c72hps45n0v5's wallet worked with streaming sats for Podcasting 2.0. But now NWC is coming to Fountain, and users can bring their own wallet that they control.
The future of NWC is bright, and it extends well beyond zapping memes on Nostr. It's going to open up a world of possibilities for how we can use our sats to stream media, make reoccurring donations, use micro-payments to rent compute, and so much more. I don't know about you, but I am here for it!
-
 @ dd664d5e:5633d319
2025-03-21 12:22:36
@ dd664d5e:5633d319
2025-03-21 12:22:36Men tend to find women attractive, that remind them of the average women they already know, but with more-averaged features. The mid of mids is kween.👸
But, in contradiction to that, they won't consider her highly attractive, unless she has some spectacular, unusual feature. They'll sacrifice some averageness to acquire that novelty. This is why wealthy men (who tend to be highly intelligent -- and therefore particularly inclined to crave novelty because they are easily bored) -- are more likely to have striking-looking wives and girlfriends, rather than conventionally-attractive ones. They are also more-likely to cross ethnic and racial lines, when dating.
Men also seem to each be particularly attracted to specific facial expressions or mimics, which might be an intelligence-similarity test, as persons with higher intelligence tend to have a more-expressive mimic. So, people with similar expressions tend to be on the same wavelength. Facial expessions also give men some sense of perception into womens' inner life, which they otherwise find inscrutable.
Hair color is a big deal (logic says: always go blonde), as is breast-size (bigger is better), and WHR (smaller is better).

-
 @ da0b9bc3:4e30a4a9
2025-03-28 07:27:06
@ da0b9bc3:4e30a4a9
2025-03-28 07:27:06Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/927569
-
 @ 502ab02a:a2860397
2025-03-28 04:57:18
@ 502ab02a:a2860397
2025-03-28 04:57:18จริงหรือ ว่าโอเมก้า3 ต้องมาจากปลาทะเลเท่านั้น
มีเรื่องที่น่าสนใจเรื่องนึงครับ ถ้าพูดถึงโอเมก้า-3 หลายคนอาจนึกถึงปลาทะเลน้ำลึก เช่น แซลมอน แมคเคอเรล หรือซาร์ดีน ซึ่งเป็นแหล่งโอเมก้า-3 ที่ร่างกายใช้ได้ดี แต่ในขณะเดียวกัน ก็มีกลุ่มคนที่พยายามบริโภคโอเมก้า-3 จากพืชแทน เช่น น้ำมันเมล็ดแฟลกซ์ น้ำมันเมล็ดเจีย หรือวอลนัท โดยหวังว่าจะได้รับประโยชน์เช่นเดียวกับการกินปลา แต่ที่เราเรียนรู้กันมาว่า โอเมก้า-3 จากพืชนั้น ร่างกายมนุษย์นำไปใช้ได้น้อยมาก หรือแทบไม่ได้เลย
สาเหตุหลักมาจากรูปแบบของโอเมก้า-3 ที่พบในแหล่งต่างๆ โอเมก้า-3 มีอยู่ 3 ชนิดหลัก ได้แก่ ALA (Alpha-Linolenic Acid) – พบในพืช EPA (Eicosapentaenoic Acid) – พบในปลาทะเล DHA (Docosahexaenoic Acid) – พบในปลาทะเล
ร่างกายสามารถใช้ EPA และ DHA ได้โดยตรง แต่สำหรับ ALA นั้น ร่างกายต้องผ่านกระบวนการเปลี่ยนแปลงทางชีวเคมีก่อน ซึ่งกระบวนการนี้ไม่มีประสิทธิภาพนัก โดยทั่วไปแล้ว ALA แปลงเป็น EPA ได้เพียง 5-10% ALA แปลงเป็น DHA ได้เพียง 0.5-5% แปลว่า หากคุณกินเมล็ดแฟลกซ์หรือน้ำมันเมล็ดเจีย แม้ว่าจะมีปริมาณ ALA สูง แต่ร่างกายก็แทบไม่ได้รับ EPA และ DHA ในปริมาณที่เพียงพอเพื่อใช้ประโยชน์อย่างเต็มที่
ทำไมร่างกายแปลง ALA เป็น EPA/DHA ได้น้อย? อันแรกเลยคือ เอนไซม์จำกัด กระบวนการเปลี่ยน ALA เป็น EPA และ DHA จะใช้เอนไซม์เดียวกับการแปลงโอเมก้า-6 ซึ่งมักถูกใช้ไปกับโอเมก้า-6 ที่มากเกินไปในอาหารปัจจุบันซะแล้วนั่นเอง ต่อมาคือ กระบวนการหลายขั้นตอน การเปลี่ยน ALA เป็น DHA ต้องผ่านหลายขั้นตอนทางชีวเคมี ทำให้มีการสูญเสียพลังงานและวัตถุดิบไปมาก และสุดท้าย ปัจจัยทางพันธุกรรมและเพศ บางคน โดยเฉพาะผู้หญิง อาจมีอัตราการเปลี่ยนที่สูงกว่าผู้ชายเล็กน้อย แต่ก็ยังต่ำเมื่อเทียบกับการได้รับ EPA/DHA จากปลาหรือสาหร่ายโดยตรง
โอเมก้า-6 ตัวการขัดขวางโอเมก้า-3 จากพืช โอเมก้า-6 เป็นกรดไขมันจำเป็นที่พบมากในน้ำมันพืช เช่น น้ำมันถั่วเหลือง น้ำมันข้าวโพด และน้ำมันดอกทานตะวัน ซึ่งเป็นส่วนประกอบหลักของอาหารแปรรูปในปัจจุบัน ปัญหาคือ เอนไซม์ที่ใช้แปลง ALA ไปเป็น EPA/DHA เป็นตัวเดียวกับที่ใช้แปลงโอเมก้า-6 ไปเป็น AA (Arachidonic Acid) ซึ่งมีบทบาทในการอักเสบ หากเราบริโภคโอเมก้า-6 มากเกินไป (ซึ่งคนส่วนใหญ่ทำ5555) เอนไซม์เหล่านี้จะถูกใช้ไปกับโอเมก้า-6 มากกว่า ทำให้ ALA มีโอกาสแปลงเป็น EPA/DHA น้อยลงไปอีก
แล้วคนที่ไม่กินปลาหรือชาววีแกนควรทำอย่างไร? สำหรับคนที่ไม่สามารถหรือไม่ต้องการกินปลา ก็จะมีการบริโภคน้ำมันสาหร่ายที่มี DHA โดยตรงเป็นทางเลือกที่ดีกว่าการหวังพึ่ง ALA จากพืช เพราะ DHA จากสาหร่ายสามารถดูดซึมและใช้ได้ทันทีเหมือน DHA จากปลา
ได้ด้วยเหรอ ????? ผมเล่ากำเนิดของ DHA ในปลาให้ประมาณนี้ครับ จริง ๆ แล้ว DHA ซึ่งเป็นโอเมก้า-3 ที่ร่างกายใช้ได้โดยตรง มาจาก Docosahexaenoic Acid ที่เกิดจากกระบวนการสังเคราะห์ตามธรรมชาติ ซึ่งสาหร่ายบางสายพันธุ์ เช่น Schizochytrium และ Crypthecodinium cohnii มีเอนไซม์ที่สามารถเปลี่ยนกรดไขมันพื้นฐานให้กลายเป็น DHA ได้เองซึ่งเป็นส่วนประกอบหลักในระบบนิเวศทะเล(พืชกักเก็บไขมันได้อย่างไร ผมเคยโพสไปแล้ว) โดยเฉพาะ สาหร่ายขนาดเล็ก (microalgae) สาหร่ายจึงเป็นสิ่งมีชีวิตในทะเลพัฒนาให้มี DHA สูงเพราะ DHA เป็นส่วนประกอบสำคัญที่ช่วยรักษาความยืดหยุ่นและความสมบูรณ์ของเยื่อหุ้มเซลล์ในสาหร่าย ทำให้พวกมันสามารถดำรงชีวิตในสภาพแวดล้อมที่มีอุณหภูมิต่ำในทะเลได้
จากนั้นก็เป็นไปตามห่วงโซ่อาหารครับ ปลาและสัตว์ทะเลอื่น ๆ ได้รับ DHA จากการบริโภคสาหร่ายหรือสัตว์เล็ก ๆ ที่กินสาหร่ายมาอีกที ดังนั้น DHA ในปลาเป็นผลมาจากการสะสมจากสาหร่ายโดยตรง นี่เป็นเหตุผลว่าทำไมปลาทะเลน้ำลึก เช่น แซลมอน แมคเคอเรล และซาร์ดีน ถึงมี DHA สูงนั่นเอง งว่ออออออ
ดังนั้น เมื่อคุณกิน DHA จากสาหร่าย ก็เท่ากับว่าคุณได้รับ DHA จากต้นกำเนิดแท้จริงในระบบนิเวศทะเลครับ DHA ที่ได้มาจากสาหร่ายสามารถนำไปใช้ในร่างกายได้ทันทีโดยไม่ต้องผ่านกระบวนการเปลี่ยนแปลง เพราะมันอยู่ในรูป Triglyceride หรือ Phospholipid ซึ่งเป็นรูปแบบที่ร่างกายมนุษย์สามารถดูดซึมและนำไปใช้ได้ทันที ปลาไม่ได้แปลงโครงสร้าง DHA แต่เพียงสะสม DHA ไว้ในตัวจากการกินสาหร่าย ดังนั้นการรับประทาน DHA จากสาหร่ายก็ให้ผลเทียบเท่ากับการรับประทาน DHA จากปลา งานวิจัยหลายฉบับยืนยันว่า DHA จากสาหร่ายมีค่าการดูดซึม (Bioavailability) ใกล้เคียงกับ DHA จากน้ำมันปลา แต่หาเอาเองนะถ้าอยากอ่านฉบับเต็ม
การผลิตน้ำมันสาหร่ายนั้น เมื่อสาหร่ายเจริญเติบโตเต็มที่แล้ว เขาจะทำการเก็บเกี่ยวและสกัดน้ำมันโดยใช้เทคโนโลยีการแยกที่ทันสมัย ซึ่งช่วยรักษาให้ DHA ที่มีอยู่ในเซลล์สาหร่ายถูกเก็บรักษาไว้ในรูปแบบที่สามารถนำไปใช้ได้โดยตรง จากนั้นจะเข้าสู่การกรองหรือการปั่นแยก (centrifugation) เพื่อให้ได้มวลสาหร่ายที่เข้มข้น จากนั้นจึงทำให้แห้งเพื่อเตรียมเข้าสู่กระบวนการสกัด ซึ่งมีหลายวิธีอาทิเช่น
1 การสกัดด้วยตัวทำละลาย
ใช้ตัวทำละลาย เช่น เฮกเซน (Hexane) หรือ เอทานอล (Ethanol) เพื่อสกัดน้ำมันออกจากเซลล์สาหร่าย จากนั้นน้ำมันจะถูกนำไปกลั่นเพื่อแยกตัวทำละลายออก ทำให้ได้น้ำมันที่มีความบริสุทธิ์สูง 2. การสกัดด้วย CO₂ เหลว ใช้ คาร์บอนไดออกไซด์ในสถานะวิกฤติ (Supercritical CO₂) ซึ่งเป็นวิธีที่ทันสมัย ก๊าซ CO₂ จะถูกทำให้มีความดันสูงและอุณหภูมิที่เหมาะสมเพื่อกลายเป็นของเหลว แล้วใช้แยกน้ำมันออกจากเซลล์สาหร่าย วิธีนี้ช่วยให้ได้น้ำมันที่ ปราศจากตัวทำละลายเคมีและมีความบริสุทธิ์สูง 3. การสกัดด้วยการกดอัด หรือ Cold Pressed
เป็นวิธีที่ใช้แรงดันทางกลกดเซลล์สาหร่ายเพื่อให้ได้น้ำมันออกมา อันนี้เป็นการผลิตน้ำมันแบบออร์แกนิกเลยครับ แต่ให้ผลผลิตน้อยกว่าวิธีอื่น ๆน้ำมันที่ได้จากการสกัดจะผ่านการกลั่นด้วยกระบวนการต่าง ๆ เช่น Winterization กำจัดไขมันที่ไม่จำเป็น Molecular Distillation แยกสารตกค้าง เช่น โลหะหนักและสารปนเปื้อน Deodorization กำจัดกลิ่นคาวของสาหร่าย จากนั้นก็บรรจุใส่ซอฟท์เจล พร้อมจำหน่ายนั่นเองครับ
ก็ถือว่าเป็นอีกทางเลือกของชาววีแกน ที่ไม่สามารถกินปลาหรือสัตว์ทะเลได้ ก็น่าจะเฮกันดังๆได้เลยครับ จะได้มีตัวช่วยในการลดการอักเสบได้
ส่วนชาว food matrix ก็ต้องเรียนรู้ระบบครับ การกินจากปลาหรือสัตว์ทะเล ก็จะได้โปรตีน แร่ธาตุ วิตามินอื่นๆควบมากับตัวสัตว์ตามที่ธรรมชาติแพคมาให้ ถ้าจะเสริมเป็นน้ำมันสาหร่าย ก็สุดแล้วแต่ความต้องการครับ ไม่ใช่เรื่องแย่อะไร เว้นแต่ไปเทียบราคาเอาเองนะ 55555
#pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ a3bb06f6:19ac1b11
2025-03-28 02:36:38
@ a3bb06f6:19ac1b11
2025-03-28 02:36:38“Until you make the unconscious conscious, it will continue to direct your life, and you will call it fate.” — Carl Jung
Most people don’t realize they’ve been robbed. Not in the dramatic, wallet-snatching sense, but in a quiet, systemic way that’s gone unnoticed for generations. If you’re feeling like no matter how hard you work, you can’t get ahead… you’re not imagining it.
It didn’t start as a scheme—but one compromise after another, it became one. Now, the system exploits you by design. This isn’t fate. It’s fiat.
The Unconscious Script: How Fiat Becomes Invisible From the moment you're born, you're placed into an economic system based on government-issued fiat currency. It becomes the air you breathe. You work for dollars. You save in dollars. You price your time, your future, and even your dreams in dollars.
But few stop to ask: What actually is a dollar? Who creates it? Why does it lose value?
This lack of questioning is the unconscious state. Fiat money is the background process running your life. You feel the effects—rising prices, shrinking savings, mounting debt—but you never see the root cause. So you blame yourself. Or “the economy.” Or call it fate.
The Lie of Neutral Money: Most believe money is just a neutral tool. But fiat is not neutral—it’s political power encoded into paper.
Governments can print more of it at will. Central banks can manipulate its supply, distort interest rates, and quietly tax you through inflation. Every time more money is created, your purchasing power shrinks.
But it happens slowly, like a leak in a tire. You don’t notice at first. You just feel like you’re working harder for less. The house is further out of reach. The groceries cost more. Retirement feels impossible.
And you accept it. Because no one told you it's designed this way.

Inflation Is the Invisible Thief, Inflation isn’t just a “cost of living increase.” It’s a state-sponsored form of theft.
When new money is created, it enters the system unevenly. Those closest to the money printer—banks, governments, large corporations—get the new dollars first. By the time it reaches you, prices have already risen. You’re buying the same goods with weaker money.
And yet, most people still save in fiat. They’re taught that hoarding cash is “safe.” They’re taught that 2% inflation is “normal.” But it’s not normal to work 40 hours a week and fall behind. That’s the product of unconscious acceptance.
The fiat system survives on one thing: your ignorance. It didn’t begin with malicious intent, but over time, it adapted to protect its own power—at your expense. As long as you don’t understand how money works, you won’t resist. You’ll blame yourself, or capitalism, or bad luck. But never the system itself.
This is why financial education is never prioritized in schools. This is why questioning monetary policy is left to economists and suits on CNBC. You were never taught how it works. And now the system depends on you staying confused—grinding, borrowing, complying, without ever asking why.
Making the Unconscious Conscious: Enter Bitcoin, Bitcoin breaks this spell.

It forces you to confront the nature of money—what it is, how it’s created, and why fiat fails. It teaches you that money doesn’t need to be printed, inflated, or controlled. That money can be fixed, finite, and fair.
Bitcoin is not just a new currency. It’s a tool of consciousness. It exposes the scam of fiat and offers a lifeboat to anyone ready to wake up.
Once you understand Bitcoin, you can’t unsee the problem. You begin to ask:
Why should I trust a system that steals my time? Why is saving discouraged, but debt rewarded? Why do I need permission to use my own money? These aren’t technical questions. They’re moral ones.
Consciousness Is Sovereignty: When you understand what fiat is, you stop calling your financial struggles “fate.” You start calling them what they are, outcomes of a broken system.
And once you see the system for what it is, you can choose to exit.

Saving in Bitcoin is not speculation. It’s self-defense. It’s rejecting unconscious servitude. It’s reclaiming your time, your labor, your future.
In a fiat world, they own the money—so they own the rules. In a Bitcoin world, you own yourself.
That’s the power of making the unconscious conscious.
And that’s how you stop calling it fate.
-
 @ aa8de34f:a6ffe696
2025-03-21 12:08:31
@ aa8de34f:a6ffe696
2025-03-21 12:08:3119. März 2025
🔐 1. SHA-256 is Quantum-Resistant
Bitcoin’s proof-of-work mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, SHA-256 remains secure because:
- Quantum computers excel at factoring large numbers (Shor’s Algorithm).
- However, SHA-256 is a one-way function, meaning there's no known quantum algorithm that can efficiently reverse it.
- Grover’s Algorithm (which theoretically speeds up brute force attacks) would still require 2¹²⁸ operations to break SHA-256 – far beyond practical reach.
++++++++++++++++++++++++++++++++++++++++++++++++++
🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses
Bitcoin uses Elliptic Curve Digital Signature Algorithm (ECDSA) to generate keys.
- A quantum computer could use Shor’s Algorithm to break SECP256K1, the curve Bitcoin uses.
- If you never reuse addresses, it is an additional security element
- 🔑 1. Bitcoin Addresses Are NOT Public Keys
Many people assume a Bitcoin address is the public key—this is wrong.
- When you receive Bitcoin, it is sent to a hashed public key (the Bitcoin address).
- The actual public key is never exposed because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend
- Bitcoin uses Pay-to-Public-Key-Hash (P2PKH) or newer methods like Pay-to-Witness-Public-Key-Hash (P2WPKH), which add extra layers of security.
🕵️♂️ 2.1 The Public Key Never Appears
- When you send Bitcoin, your wallet creates a digital signature.
- This signature uses the private key to prove ownership.
- The Bitcoin address is revealed and creates the Public Key
- The public key remains hidden inside the Bitcoin script and Merkle tree.
This means: ✔ The public key is never exposed. ✔ Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.
+++++++++++++++++++++++++++++++++++++++++++++++++
🔄 3. Bitcoin Can Upgrade
Even if quantum computers eventually become a real threat:
- Bitcoin developers can upgrade to quantum-safe cryptography (e.g., lattice-based cryptography or post-quantum signatures like Dilithium).
- Bitcoin’s decentralized nature ensures a network-wide soft fork or hard fork could transition to quantum-resistant keys.
++++++++++++++++++++++++++++++++++++++++++++++++++
⏳ 4. The 10-Minute Block Rule as a Security Feature
- Bitcoin’s network operates on a 10-minute block interval, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack every 10 minutes.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system resets the challenge with every new block.This limits the window of opportunity for quantum attacks.
🎯 5. Quantum Attack Needs to Solve a Block in Real-Time
- A quantum attacker must solve the cryptographic puzzle (Proof of Work) in under 10 minutes.
- The problem? Any slight error changes the hash completely, meaning:If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails.Quantum decoherence (loss of qubit stability) makes error correction a massive challenge.The computational cost of recovering from an incorrect hash is still incredibly high.
⚡ 6. Network Resilience – Even if a Block Is Hacked
- Even if a quantum computer somehow solved a block instantly:The network would quickly recognize and reject invalid transactions.Other miners would continue mining under normal cryptographic rules.51% Attack? The attacker would need to consistently beat the entire Bitcoin network, which is not sustainable.
🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats
- Bitcoin adjusts mining difficulty every 2016 blocks (\~2 weeks).
- If quantum miners appeared and suddenly started solving blocks too quickly, the difficulty would adjust upward, making attacks significantly harder.
- This self-correcting mechanism ensures that even quantum computers wouldn't easily overpower the network.
🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin
✔ The 10-minute rule limits attack frequency – quantum computers can’t keep up.
✔ Any slight miscalculation ruins the attack, resetting all progress.
✔ Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages.
Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant. 🚀
-
 @ 1c19eb1a:e22fb0bc
2025-03-21 00:34:10
@ 1c19eb1a:e22fb0bc
2025-03-21 00:34:10What is #Nostrversity? It's where you can come to learn about all the great tools, clients, and amazing technology that is being built on #Nostr, for Nostr, or utilized by Nostr, presented in an approachable and non-technical format. If you have ever wondered what Blossom, bunker signing, or Nostr Wallet Connect are, how they work, and how you can put them to work to improve your Nostr experience, this is the place you can read about them without needing a computer-science degree ahead of time.
Between writing full-length reviews, which take a fair amount of time to research, test, and draft, I will post shorter articles with the Nostrversity hashtag to provide a Nostr-native resource to help the community understand and utilize the tools our illustrious developers are building. These articles will be much shorter, and more digestible than my full-length reviews. They will also cover some things that may not be quite ready for prime-time, whereas my reviews will continue to focus on Nostr apps that are production-ready.
Keep an eye out, because Nostr Wallet Connect will be the first topic of study. Take your seats, get out your notepads, and follow along to discover how Nostr Wallet Connect is improving Lightning infrastructure. Hint: It's not just for zaps.
-
 @ 84b0c46a:417782f5
2025-03-27 23:52:24
@ 84b0c46a:417782f5
2025-03-27 23:52:24nostr:nevent1qqsw9v8usvahkqmmc9qavu6g834v09j6e2u2acdua24tk73dqc05xecgkanse
-
 @ 878dff7c:037d18bc
2025-03-27 22:37:47
@ 878dff7c:037d18bc
2025-03-27 22:37:47Australian Prime Minister Calls Election Amid Economic Challenges
Summary:
Prime Minister Anthony Albanese has announced that Australia will hold federal elections on May 3. The election comes at a time when the nation faces significant economic uncertainties, including high inflation rates, elevated interest rates, and a housing crisis. Albanese's Labor government emphasizes plans for economic recovery, while opposition leader Peter Dutton's Coalition proposes public sector cuts and temporary fuel duty reductions. Both leaders are striving to address voter concerns over the cost-of-living crisis and economic stability.
Sources: The Guardian - March 28, 2025, AP News - March 28, 2025
Bill Gates Predicts AI to Replace Doctors and Teachers Within 10 Years
Summary:
Bill Gates forecasts that artificial intelligence (AI) will significantly reduce human involvement in fields like medicine and education over the next decade. He envisions AI providing free, high-quality medical advice and tutoring, thereby democratizing access to these services. While acknowledging concerns about misinformation and rapid AI development, Gates remains optimistic about AI's potential to drive breakthroughs in healthcare, climate solutions, and education. He encourages young people to engage in AI-centric ventures, highlighting its transformative impact on industries and society.
Sources: New York Post - March 27, 2025
AI Poised to Transform Legal Profession by 2035
Summary:
Artificial general intelligence (AGI) is projected to render traditional lawyer roles obsolete by 2035. AI systems are advancing to perform complex legal tasks such as advising, negotiating, and dispute resolution. While some legal professionals argue that AI cannot replicate human judgment and creativity, the emphasis on efficiency and outcomes suggests a future where AGI dominates legal services with minimal human intervention. Legal industry leaders are urged to prepare for this disruptive shift.
Sources: The Times - March 28, 2025
Queensland Faces Severe Flooding as Inland 'Sea' Emerges
Summary:
Severe weather conditions, including heavy rain and potential flash flooding, have impacted central and southern inland Queensland, with significant rainfall between 200 to 400mm recorded. Towns like Adavale are inundated, prompting emergency warnings and the establishment of refuges for affected residents. Authorities urge residents to stay updated and follow safety advice.
Sources: News.com.au - 28 March 2025, The Courier-Mail - 28 March 2025, The Guardian - 28 March 2025
Opposition Leader Peter Dutton Outlines Election Platform
Summary:
Opposition Leader Peter Dutton has presented his vision for Australia, promising significant funding for defense and proposing a new gas reservation policy aimed at lowering electricity prices. The Coalition's plans include fast-tracking gas projects, investing $1 billion in gas infrastructure, reducing public service staffing by 41,000 while preserving essential services, and decreasing permanent migration intake by 25% to increase housing supply. Dutton also announced reinstating subsidized mental health visits and new spending on youth mental health.
Sources: The Guardian - March 28, 2025, The Australian - March 28, 2025
Opposition Leader Promises Significant Defense Funding
Summary:
Peter Dutton, in his budget reply, promised significant funding for defense and a new gas reservation policy for the east coast, aimed at lowering electricity prices. The Coalition also plans to fast-track gas projects and invest $1 billion in gas infrastructure. Dutton announced slashing 41,000 public service workers while preserving essential services, and criticized Labor's gas policy. Immigration plans include reducing the permanent migration intake by 25% to increase housing supply. Dutton also proposed reinstating subsidized mental health visits and new spending on youth mental health. Labor, represented by Jason Clare, argued that the Coalition's policies, including the nuclear plan, are costly and criticized the tax implications under Dutton.
Sources: The Guardian - March 28, 2025
Israeli Politicians Urge Australian MPs to Abandon Two-State Solution Policy
Summary:
A group of Israeli Knesset members has called on Australian MPs to drop support for a two-state solution between Israel and Palestine. The letter, presented during an event at Australia's Parliament House, argues that establishing a Palestinian state could lead to Israel's destruction, citing recent conflicts as evidence. This appeal reflects deep skepticism within Israeli political circles about the viability of the peace process.
Sources: The Guardian - March 27, 2025
Stephen Jones Criticizes U.S. Protectionist Trade Policies
Summary:
Outgoing Financial Services Minister Stephen Jones has criticized recent U.S. protectionist measures, including a 25% tariff on global car imports and Australian aluminum and steel. Jones emphasized the importance of open trade and a rules-based order for Australia's economic growth, highlighting concerns about the negative impact on Australian industries and the broader economy.
Sources: The Australian - March 28, 2025
New Anti-Smoking Warnings Criticized for Potential Backfire
Summary:
Starting April 1, Australia will implement legislation requiring health warnings on individual cigarettes, with messages like "causes 16 cancers" and "poisons in every puff." However, social media users have mocked these warnings, suggesting they might make smoking appear "cool" and collectible rather than serving as deterrents. Despite the criticism, health officials assert that such on-product messages are part of a broader strategy to reduce smoking rates, citing positive results from similar approaches in Canada. The initiative aims to decrease the annual tobacco-related deaths in Australia, which currently exceed 24,000.
Sources: The Courier-Mail - March 28, 2025
'Joe's Law' Introduced to Ban Future Hospital Privatization in NSW
Summary:
The New South Wales government has announced "Joe's Law," a reform to prohibit the future privatization of acute public hospitals. This decision follows the death of two-year-old Joe Massa, who suffered a cardiac arrest and died after a prolonged wait in the emergency department of the privately managed Northern Beaches Hospital. The legislation aims to ensure that critical public services like emergency and surgical care remain under public control, preventing privatization. Additionally, a parliamentary inquiry into the hospital's services and a coronial investigation into Joe's death have been initiated.
Sources: The Guardian - March 28, 2025, news.com.au - March 28, 2025, The Daily Telegraph - March 28, 2025
Determined Daisy Marks Major Milestone
Summary:
Daisy, born with a rare chromosomal disorder, has achieved a significant health milestone by having her tracheostomy removed and is now learning to communicate using sign language. Her inspiring journey is one of several highlighted by the Good Friday Appeal, which supports the Royal Children's Hospital (RCH). The 2025 Appeal aims to fund further programs, research, and vital equipment at RCH, with contributions from events like North Melbourne's SuperClash fundraiser bringing joy to young patients ahead of the marquee match.
Sources: Herald Sun - March 27, 2025
Indonesia Seeks to Calm Investors After Stocks, Rupiah Slide
Summary:
Indonesian officials are working to reassure investors following significant declines in the stock market and the rupiah. President Prabowo Subianto plans to meet with investors after the Eid-al-Fitr holiday to address concerns about government policies and fiscal stability. The rupiah recently hit its weakest level since 1998, and the main stock index fell 7.1%. Analysts attribute the selloff to poor communication on fiscal policies. The government aims to maintain the fiscal deficit within 3% of GDP and avoid political interference in its sovereign wealth fund. Efforts are also underway to deregulate the manufacturing sector and provide credits to labor-intensive industries. Bank Indonesia is prepared to intervene to stabilize the currency, emphasizing the economy's underlying strength. The rupiah has shown signs of recovery, and measures include easing buyback processes and offering more attractive investment instruments. Markets will monitor the mid-year budget update in July for signs of revenue shortfalls and spending adjustments.
Sources: Reuters - 28 March 2025
Beijing to Escalate Taiwan Coercion in 2025
Summary:
A report by the Office of the Director of National Intelligence highlights growing cooperation among China, Russia, Iran, and North Korea, posing significant challenges to U.S. global power. Closer ties between China and Russia, in particular, could present enduring risks to U.S. interests. The document points out China's military threat to the U.S., emphasizing its grey zone tactics and potential for stronger coercive action against Taiwan by 2025. The Ukraine conflict and its ongoing strategic risks, including nuclear escalation, are noted, as well as China's ambition to dominate AI by 2030 and its control over critical materials. The report also mentions the volatile Middle East, with Iran's expanding ties despite challenges, and North Korea's commitment to enhancing its nuclear capabilities. Additionally, threats from foreign drug actors and Islamic extremists, including Al-Qa'ida and a potential ISIS resurgence, are highlighted.
Sources: The Australian - 28 March 2025
Fire Ant Infestation Could Cost Australian Households Over $1 Billion Annually
Summary:
New modeling predicts that if fire ants become established in Australia, households may incur approximately $1.03 billion annually in control measures and related health and veterinary expenses. The invasive species could lead to up to 570,800 medical consultations and around 30 deaths each year due to stings. The electorates of Durack, O'Connor, Mayo, and Blair are projected to be most affected. Experts emphasize the need for increased federal funding for comprehensive eradication programs to prevent environmental damage and significant economic burdens on households.
Sources: The Guardian - March 28, 2025
The Great Monetary Divide – Epi-3643
Summary:
In this episode, host Jack Spirko discusses the rapid changes occurring in the global financial landscape. He highlights the European Union's announcement, led by European Central Bank President Christine Lagarde, to implement a Central Bank Digital Currency (CBDC) across member states by the upcoming fall. Spirko expresses concern that such a move could pave the way for a social credit system similar to China's, potentially leading to increased governmental control over individual financial activities.
Conversely, the episode explores developments in the United States, where the government is reportedly adopting Bitcoin as an economic reserve and integrating stablecoins into the financial system. Spirko suggests that these actions may indicate a divergent path from other global economies, potentially fostering a more decentralized financial environment.
Throughout the episode, Spirko emphasizes the importance of understanding these shifts and encourages listeners to consider how such changes might impact personal financial sovereignty and the broader economic landscape.
Please note that this summary is based on limited information available from the episode description and may not capture all the nuances discussed in the full podcast.
Sources: The Survival Podcast - 28 March 2025, Apple Podcasts - 28 March 2025
-
 @ 16f1a010:31b1074b
2025-03-20 14:32:25
@ 16f1a010:31b1074b
2025-03-20 14:32:25grain is a nostr relay built using Go, currently utilizing MongoDB as its database. Binaries are provided for AMD64 Windows and Linux. grain is Go Relay Architecture for Implementing Nostr
Introduction
grain is a nostr relay built using Go, currently utilizing MongoDB as its database. Binaries are provided for AMD64 Windows and Linux. grain is Go Relay Architecture for Implementing Nostr
Prerequisites
- Grain requires a running MongoDB instance. Please refer to this separate guide for instructions on setting up MongoDB: nostr:naddr1qvzqqqr4gupzq9h35qgq6n8ll0xyyv8gurjzjrx9sjwp4hry6ejnlks8cqcmzp6tqqxnzde5xg6rwwp5xsuryd3knfdr7g
Download Grain
Download the latest release for your system from the GitHub releases page
amd64 binaries provided for Windows and Linux, if you have a different CPU architecture, you can download and install go to build grain from source
Installation and Execution
- Create a new folder on your system where you want to run Grain.
- The downloaded binary comes bundled with a ZIP file containing a folder named "app," which holds the frontend HTML files. Unzip the "app" folder into the same directory as the Grain executable.
Run Grain
- Open your terminal or command prompt and navigate to the Grain directory.
- Execute the Grain binary.
on linux you will first have to make the program executable
chmod +x grain_linux_amd64Then you can run the program
./grain_linux_amd64(alternatively on windows, you can just double click the grain_windows_amd64.exe to start the relay)
You should see a terminal window displaying the port on which your relay and frontend are running.
If you get
Failed to copy app/static/examples/config.example.yml to config.yml: open app/static/examples/config.example.yml: no such file or directory
Then you probably forgot to put the app folder in the same directory as your executable or you did not unzip the folder.
Congrats! You're running grain 🌾!
You may want to change your NIP11 relay information document (relay_metadata.json) This informs clients of the capabilities, administrative contacts, and various server attributes. It's located in the same directory as your executable.
Configuration Files
Once Grain has been executed for the first time, it will generate the default configuration files inside the directory where the executable is located. These files are:
bash config.yml whitelist.yml blacklist.ymlPrerequisites: - Grain requires a running MongoDB instance. Please refer to this separate guide for instructions on setting up MongoDB: [Link to MongoDB setup guide].
Download Grain:
Download the latest release for your system from the GitHub releases page
amd64 binaries provided for Windows and Linux, if you have a different CPU architecture, you can download and install go to build grain from source
Installation and Execution:
- Create a new folder on your system where you want to run Grain.
- The downloaded binary comes bundled with a ZIP file containing a folder named "app," which holds the frontend HTML files. Unzip the "app" folder into the same directory as the Grain executable.
Run Grain:
- Open your terminal or command prompt and navigate to the Grain directory.
- Execute the Grain binary.
on linux you will first have to make the program executable
chmod +x grain_linux_amd64Then you can run the program
./grain_linux_amd64(alternatively on windows, you can just double click the grain_windows_amd64.exe to start the relay)
You should see a terminal window displaying the port on which your relay and frontend are running.
If you get
Failed to copy app/static/examples/config.example.yml to config.yml: open app/static/examples/config.example.yml: no such file or directory
Then you probably forgot to put the app folder in the same directory as your executable or you did not unzip the folder.
Congrats! You're running grain 🌾!
You may want to change your NIP11 relay information document (relay_metadata.json) This informs clients of the capabilities, administrative contacts, and various server attributes. It's located in the same directory as your executable.
Configuration Files:
Once Grain has been executed for the first time, it will generate the default configuration files inside the directory where the executable is located. These files are:
bash config.yml whitelist.yml blacklist.ymlConfiguration Documentation
You can always find the latest example configs on my site or in the github repo here: config.yml
Config.yml
This
config.ymlfile is where you customize how your Grain relay operates. Each section controls different aspects of the relay's behavior.1.
mongodb(Database Settings)uri: mongodb://localhost:27017/:- This is the connection string for your MongoDB database.
mongodb://localhost:27017/indicates that your MongoDB server is running on the same computer as your Grain relay (localhost) and listening on port 27017 (the default MongoDB port).- If your MongoDB server is on a different machine, you'll need to change
localhostto the server's IP address or hostname. - The trailing
/indicates the root of the mongodb server. You will define the database in the next line.
database: grain:- This specifies the name of the MongoDB database that Grain will use to store Nostr events. Grain will create this database if it doesn't already exist.
- You can name the database whatever you want. If you want to run multiple grain relays, you can and they can have different databases running on the same mongo server.
2.
server(Relay Server Settings)port: :8181:- This sets the port on which your Grain relay will listen for incoming nostr websocket connections and what port the frontend will be available at.
read_timeout: 10 # in seconds:- This is the maximum time (in seconds) that the relay will wait for a client to send data before closing the connection.
write_timeout: 10 # in seconds:- This is the maximum time (in seconds) that the relay will wait for a client to receive data before closing the connection.
idle_timeout: 120 # in seconds:- This is the maximum time (in seconds) that the relay will keep a connection open if there's no activity.
max_connections: 100:- This sets the maximum number of simultaneous client connections that the relay will allow.
max_subscriptions_per_client: 10:- This sets the maximum amount of subscriptions a single client can request from the relay.
3.
resource_limits(System Resource Limits)cpu_cores: 2 # Limit the number of CPU cores the application can use:- This restricts the number of CPU cores that Grain can use. Useful for controlling resource usage on your server.
memory_mb: 1024 # Cap the maximum amount of RAM in MB the application can use:- This limits the maximum amount of RAM (in megabytes) that Grain can use.
heap_size_mb: 512 # Set a limit on the Go garbage collector's heap size in MB:- This sets a limit on the amount of memory that the Go programming language's garbage collector can use.
4.
auth(Authentication Settings)enabled: false # Enable or disable AUTH handling:- If set to
true, this enables authentication handling, requiring clients to authenticate before using the relay.
- If set to
relay_url: "wss://relay.example.com/" # Specify the relay URL:- If authentication is enabled, this is the url that clients will use to authenticate.
5.
UserSync(User Synchronization)user_sync: false:- If set to true, the relay will attempt to sync user data from other relays.
disable_at_startup: true:- If user sync is enabled, this will prevent the sync from starting when the relay starts.
initial_sync_relays: [...]:- A list of other relays to pull user data from.
kinds: []:- A list of event kinds to pull from the other relays. Leaving this empty will pull all event kinds.
limit: 100:- The limit of events to pull from the other relays.
exclude_non_whitelisted: true:- If set to true, only users on the whitelist will have their data synced.
interval: 360:- The interval in minutes that the relay will resync user data.
6.
backup_relay(Backup Relay)enabled: false:- If set to true, the relay will send copies of received events to the backup relay.
url: "wss://some-relay.com":- The url of the backup relay.
7.
event_purge(Event Purging)enabled: false:- If set to
true, the relay will automatically delete old events.
- If set to
keep_interval_hours: 24:- The number of hours to keep events before purging them.
purge_interval_minutes: 240:- How often (in minutes) the purging process runs.
purge_by_category: ...:- Allows you to specify which categories of events (regular, replaceable, addressable, deprecated) to purge.
purge_by_kind_enabled: false:- If set to true, events will be purged based on the kinds listed below.
kinds_to_purge: ...:- A list of event kinds to purge.
exclude_whitelisted: true:- If set to true, events from whitelisted users will not be purged.
8.
event_time_constraints(Event Time Constraints)min_created_at: 1577836800:- The minimum
created_attimestamp (Unix timestamp) that events must have to be accepted by the relay.
- The minimum
max_created_at_string: now+5m:- The maximum created at time that an event can have. This example shows that the max created at time is 5 minutes in the future from the time the event is received.
min_created_at_stringandmax_created_atwork the same way.
9.
rate_limit(Rate Limiting)ws_limit: 100:- The maximum number of WebSocket messages per second that the relay will accept.
ws_burst: 200:- Allows a temporary burst of WebSocket messages.
event_limit: 50:- The maximum number of Nostr events per second that the relay will accept.
event_burst: 100:- Allows a temporary burst of Nostr events.
req_limit: 50:- The limit of http requests per second.
req_burst: 100:- The allowed burst of http requests.
max_event_size: 51200:- The maximum size (in bytes) of a Nostr event that the relay will accept.
kind_size_limits: ...:- Allows you to set size limits for specific event kinds.
category_limits: ...:- Allows you to set rate limits for different event categories (ephemeral, addressable, regular, replaceable).
kind_limits: ...:- Allows you to set rate limits for specific event kinds.
By understanding these settings, you can tailor your Grain Nostr relay to meet your specific needs and resource constraints.
whitelist.yml
The
whitelist.ymlfile is used to control which users, event kinds, and domains are allowed to interact with your Grain relay. Here's a breakdown of the settings:1.
pubkey_whitelist(Public Key Whitelist)enabled: false:- If set to
true, this enables the public key whitelist. Only users whose public keys are listed will be allowed to publish events to your relay.
- If set to
pubkeys::- A list of hexadecimal public keys that are allowed to publish events.
pubkey1andpubkey2are placeholders, you will replace these with actual hexadecimal public keys.
npubs::- A list of npubs that are allowed to publish events.
npub18ls2km9aklhzw9yzqgjfu0anhz2z83hkeknw7sl22ptu8kfs3rjq54am44andnpub2are placeholders, replace them with actual npubs.- npubs are bech32 encoded public keys.
2.
kind_whitelist(Event Kind Whitelist)enabled: false:- If set to
true, this enables the event kind whitelist. Only events with the specified kinds will be allowed.
- If set to
kinds::- A list of event kinds (as strings) that are allowed.
"1"and"2"are example kinds. Replace these with the kinds you want to allow.- Example kinds are 0 for metadata, 1 for short text notes, and 2 for recommend server.
3.
domain_whitelist(Domain Whitelist)enabled: false:- If set to
true, this enables the domain whitelist. This checks the domains .well-known folder for their nostr.json. This file contains a list of pubkeys. They will be considered whitelisted if on this list.
- If set to
domains::- A list of domains that are allowed.
"example.com"and"anotherdomain.com"are example domains. Replace these with the domains you want to allow.
blacklist.yml
The
blacklist.ymlfile allows you to block specific content, users, and words from your Grain relay. Here's a breakdown of the settings:1.
enabled: true- This setting enables the blacklist functionality. If set to
true, the relay will actively block content and users based on the rules defined in this file.
2.
permanent_ban_words:- This section lists words that, if found in an event, will result in a permanent ban for the event's author.
- really bad wordis a placeholder. Replace it with any words you want to permanently block.
3.
temp_ban_words:- This section lists words that, if found in an event, will result in a temporary ban for the event's author.
- crypto,- web3, and- airdropare examples. Replace them with the words you want to temporarily block.
4.
max_temp_bans: 3- This sets the maximum number of temporary bans a user can receive before they are permanently banned.
5.
temp_ban_duration: 3600- This sets the duration of a temporary ban in seconds.
3600seconds equals one hour.
6.
permanent_blacklist_pubkeys:- This section lists hexadecimal public keys that are permanently blocked from using the relay.
- db0c9b8acd6101adb9b281c5321f98f6eebb33c5719d230ed1870997538a9765is an example. Replace it with the public keys you want to block.
7.
permanent_blacklist_npubs:- This section lists npubs that are permanently blocked from using the relay.
- npub1x0r5gflnk2mn6h3c70nvnywpy2j46gzqwg6k7uw6fxswyz0md9qqnhshtnis an example. Replace it with the npubs you want to block.- npubs are the human readable version of public keys.
8.
mutelist_authors:- This section lists hexadecimal public keys of author of a kind1000 mutelist. Pubkey authors on this mutelist will be considered on the permanent blacklist. This provides a nostr native way to handle the backlist of your relay
- 3fe0ab6cbdb7ee27148202249e3fb3b89423c6f6cda6ef43ea5057c3d93088e4is an example. Replace it with the public keys of authors that have a mutelist you would like to use as a blacklist. Consider using your own.- Important Note: The mutelist Event MUST be stored in this relay for it to be retrieved. This means your relay must have a copy of the authors kind10000 mutelist to consider them for the blacklist.
Running Grain as a Service:
Windows Service:
To run Grain as a Windows service, you can use tools like NSSM (Non-Sucking Service Manager). NSSM allows you to easily install and manage any application as a Windows service.
* For instructions on how to install NSSM, please refer to this article: [Link to NSSM install guide coming soon].-
Open Command Prompt as Administrator:
- Open the Windows Start menu, type "cmd," right-click on "Command Prompt," and select "Run as administrator."
-
Navigate to NSSM Directory:
- Use the
cdcommand to navigate to the directory where you extracted NSSM. For example, if you extracted it toC:\nssm, you would typecd C:\nssmand press Enter.
- Use the
-
Install the Grain Service:
- Run the command
nssm install grain. - A GUI will appear, allowing you to configure the service.
- Run the command
-
Configure Service Details:
- In the "Path" field, enter the full path to your Grain executable (e.g.,
C:\grain\grain_windows_amd64.exe). - In the "Startup directory" field, enter the directory where your Grain executable is located (e.g.,
C:\grain).
- In the "Path" field, enter the full path to your Grain executable (e.g.,
-
Install the Service:
- Click the "Install service" button.
-
Manage the Service:
- You can now manage the Grain service using the Windows Services manager. Open the Start menu, type "services.msc," and press Enter. You can start, stop, pause, or restart the Grain service from there.
Linux Service (systemd):
To run Grain as a Linux service, you can use systemd, the standard service manager for most modern Linux distributions.
-
Create a Systemd Service File:
- Open a text editor with root privileges (e.g.,
sudo nano /etc/systemd/system/grain.service).
- Open a text editor with root privileges (e.g.,
-
Add Service Configuration:
- Add the following content to the
grain.servicefile, replacing the placeholders with your actual paths and user information:
```toml [Unit] Description=Grain Nostr Relay After=network.target
[Service] ExecStart=/path/to/grain_linux_amd64 WorkingDirectory=/path/to/grain/directory Restart=always User=your_user #replace your_user Group=your_group #replace your_group
[Install] WantedBy=multi-user.target ```
- Replace
/path/to/grain/executablewith the full path to your Grain executable. - Replace
/path/to/grain/directorywith the directory containing your Grain executable. - Replace
your_userandyour_groupwith the username and group that will run the Grain service.
- Add the following content to the
-
Reload Systemd:
- Run the command
sudo systemctl daemon-reloadto reload the systemd configuration.
- Run the command
-
Enable the Service:
- Run the command
sudo systemctl enable grain.serviceto enable the service to start automatically on boot.
- Run the command
-
Start the Service:
- Run the command
sudo systemctl start grain.serviceto start the service immediately.
- Run the command
-
Check Service Status:
- Run the command
sudo systemctl status grain.serviceto check the status of the Grain service. This will show you if the service is running and any recent logs. - You can run
sudo journalctl -f -u grain.serviceto watch the logs
- Run the command
More guides are in the works for setting up tailscale to access your relay from anywhere over a private network and for setting up a cloudflare tunnel to your domain to deploy a grain relay accessible on a subdomain of your site eg wss://relay.yourdomain.com
-
 @ 16f1a010:31b1074b
2025-03-20 14:31:19
@ 16f1a010:31b1074b
2025-03-20 14:31:19Introduction
MongoDB is a popular NoSQL document database, meaning it stores data in flexible, JSON-like documents. This makes it highly scalable and adaptable for various applications. This guide will focus on installing the Community Server edition, which is free and open-source.
This article is designed for beginners and those new to MongoDB, providing a clear and concise walkthrough of the installation process. We will cover installation on both Windows and Linux operating systems.
The official MongoDB documentation on the MongoDB website is very informative and you should be able to follow their guides. This article is written to provide a brief overview and a more streamlined installation experience.
Prerequisites
MongoDB Community Server can be installed and run on a wide range of systems. While specific hardware requirements can vary based on your intended use case and the size of your database, here are the general prerequisites:
- Operating System:
- This guide will cover installation on popular versions of Windows and Linux (specifically Ubuntu/Debian). MongoDB also supports other operating systems, which you can find on the official MongoDB website.
- Storage Space:
- You'll need sufficient disk space to store your database files. The amount of space required will depend on the size of your data. It is recommended to have more storage than you think you will initially need.
- RAM:
- While MongoDB can run with minimal RAM, having more RAM will improve performance, especially for larger databases. The amount of RAM needed will depend on the size of your data.
- Basic System Knowledge:
- Familiarity with using the command line or terminal is helpful, especially for Linux installations.
- Basic understanding of file systems and directories.
Essentially, MongoDB is designed to be flexible and can run on most modern systems. As your data grows, you can always scale your hardware accordingly.
Downloading MongoDB Community Server:
To begin, you'll need to download the MongoDB Community Server installation package.
- Visit the official MongoDB download page: https://www.mongodb.com/try/download/community
On the download page, you'll see options to select the following:
- Version: Choose the desired version of MongoDB. It is generally recommended to select the latest stable release.
- Operating System: Select your operating system (Windows or Linux).
- Package: Select the appropriate package type. For Windows, it will typically be
msi. For Linux, you will choose the package type that aligns with your linux distro. For example.debfor Debian/Ubuntu or.rpmfor RedHat/Fedora.
Once you have made your selections, click the "Download" button to download the installer or package.
Installation on Windows:
Running the Installer:
-
Locate the Downloaded Installer:
- Navigate to the directory where you downloaded the MongoDB
.msiinstaller.
- Navigate to the directory where you downloaded the MongoDB
-
Run the Installer:
- Double-click the
.msifile to start the installation wizard.
- Double-click the
-
Welcome Screen:
- Click "Next" on the welcome screen.
-
License Agreement:
- Read the license agreement, check the "I accept the terms in the License Agreement" box, and click "Next."
-
Setup Type:
- Select "Custom" installation. This allows you to choose the installation location and data directory. Click "Next."
-
Installation Location:
- You can change the default installation directory if desired. Click "Next."
-
Service Configuration:
- You can choose to install MongoDB as a service. It is recommended to install as a service.
- You can also change the "Data Directory" location here. It is recommended to change this to a location such as
C:\data\db. If you do not change it here, you will need to create the data directory manually later. - Click "Next."
-
Ready to Install:
- Click "Install" to begin the installation process.
-
Complete Installation:
- Once the installation is complete, click "Finish."
Setting Environment Variables (Optional but Recommended):
Setting the
PATHenvironment variable allows you to run MongoDB commands from any command prompt window without specifying the full path to the executable.-
Open System Properties:
- Search for "Environment Variables" in the Windows Start menu and select "Edit the system environment variables."
-
Environment Variables:
- In the "System Properties" window, click the "Environment Variables..." button.
-
Edit Path Variable:
- In the "System variables" section, find the "Path" variable and click "Edit."
-
Add MongoDB Bin Directory:
- Click "New" and add the path to the MongoDB
bindirectory. This is typicallyC:\Program Files\MongoDB\Server\<version>\bin, replacing<version>with your installed version. - Click "OK" on all open windows to save the changes.
- Click "New" and add the path to the MongoDB
-
Verify Path:
- Open a new command prompt window and type
mongod --version. If MongoDB is installed correctly and thePATHvariable is set, you should see the MongoDB version information.
- Open a new command prompt window and type
Installation on Linux (Ubuntu/Debian):
These instructions are specifically for Debian-based systems like Ubuntu.
Importing the MongoDB Public GPG Key:
-
Open a Terminal:
- Open your terminal application.
-
Import the GPG Key:
- Run the following command to import the MongoDB public GPG key:
bash wget -qO - [https://www.mongodb.org/static/pgp/server-7.0.asc](https://www.mongodb.org/static/pgp/server-7.0.asc) | sudo apt-key add -- This command downloads the GPG key and adds it to your system's trusted keys. This ensures that the packages you download from the MongoDB repository are authentic.
Adding the MongoDB Repository:
-
Add the Repository:
- Run the following command to add the MongoDB repository to your system's sources list:
bash echo "deb [ arch=amd64,arm64 ] [https://repo.mongodb.org/apt/ubuntu](https://repo.mongodb.org/apt/ubuntu) $(lsb_release -cs)/mongodb-org/7.0 multiverse" | sudo tee /etc/apt/sources.list.d/mongodb-org-7.0.list- This command adds the MongoDB repository to your system's package manager sources. The
$(lsb_release -cs)part automatically determines your Ubuntu/Debian version.
-
Update Package List:
- Run the following command to update your package list:
bash sudo apt update- This command refreshes the package list, including the newly added MongoDB repository.
Installing MongoDB:
-
Install MongoDB:
- Run the following command to install the MongoDB Community Server:
bash sudo apt install mongodb-org- This command downloads and installs the MongoDB packages.
After install, linux and windows should both have a system service already setup from the install process. You can check if it's running on linux with
sudo systemctl status mongod. On Windows, you should see the service running as "MongoDB Server" if you open system services on WindowsBasic MongoDB Commands:
After installing and starting MongoDB, you can use the
mongoshell to interact with your database. Here are some basic commands to get you started:Checking MongoDB Version:
First, let's verify that MongoDB is installed correctly by checking its version:
-
Open a Terminal or Command Prompt:
- Open your terminal (Linux/macOS) or command prompt (Windows).
-
Run
mongosh --version:- Type
mongosh --versionand press Enter. - This command will display the installed MongoDB version if it's correctly installed and in your system's PATH.
- Type
Basic MongoDB Shell Commands:
-
Open the
mongoshShell:- Type
mongoshand press Enter. This will open the MongoDB shell, and you'll see a prompt like>.
- Type
-
Show Databases:
- To see a list of all databases on your MongoDB server, type
show dbsand press Enter. - This will display a list of database names.
- To see a list of all databases on your MongoDB server, type
-
Use a Database:
- To switch to a specific database, type
use <database_name>and press Enter. Replace<database_name>with the name of the database you want to use. - Example:
use mydatabase - If the database doesn't exist, MongoDB will create it when you first store data in it.
- To switch to a specific database, type
-
Show Collections:
- After switching to a database, you can see a list of collections (similar to tables in relational databases) in that database by typing
show collectionsand pressing Enter. - Collections are where you store documents (JSON-like data).
- After switching to a database, you can see a list of collections (similar to tables in relational databases) in that database by typing
Example Session:
```bash
mongosh Current Mongosh Log ID: 6563728637951a37887e2730 Connecting to: mongodb://127.0.0.1:27017/?directConnection=true&serverSelectionTimeoutMS=2000&appName=mongosh Using MongoDB: 7.0.3 Using Mongosh: 2.1.1 For mongosh info see: https://docs.mongodb.com/mongodb-shell/
test> show dbs admin 40 KiB config 72 KiB local 40 KiB test> use mydatabase switched to db mydatabase mydatabase> show collections mydatabase> ```
Conclusion
Congratulations! You have successfully installed and started MongoDB Community Server. You've learned how to download, install, and run MongoDB on both Windows and Linux systems, and you've explored some basic commands to interact with your database.
Now, you might want to try an application like grain, a Nostr relay, which utilizes MongoDB as its database. Learn How to Install grain: nostr:naddr1qvzqqqr4gupzq9h35qgq6n8ll0xyyv8gurjzjrx9sjwp4hry6ejnlks8cqcmzp6tqqxnzde5xg6rqdpnx56rqv34uyz5g4
Remember, this guide covers the basics. There's much more to explore in the world of MongoDB, including advanced querying, indexing, replication, and sharding. Continue exploring the official MongoDB documentation to deepen your knowledge and unlock the full potential of this powerful database.
- Operating System:
-
 @ f1989a96:bcaaf2c1
2025-03-20 14:21:35
@ f1989a96:bcaaf2c1
2025-03-20 14:21:35Good morning, readers!
In Thailand, the government announced a third digital cash handout to “stimulate the economy and drive technological adoption.” This disbursement will allocate 27 billion baht ($800 million) to 2.7 million citizens aged 16-20. Like in previous phases, it will be distributed via a state-controlled “digital wallet” application, which essentially functions as a central bank digital currency (CBDC). This system gives the regime an inside view of Thais’ financial activity and creates a centralized database to monitor, censor, and control.
Meanwhile, in Russia, the central bank has proposed limiting Bitcoin access to only the wealthiest individuals. Under the proposal, only Russians with over $1.2 million in assets or an annual income above $580,000 could buy and sell digital assets — arbitrarily barring everyday Russians (including obviously most journalists and activists) from accessing Bitcoin and the financial independence it grants.
In open-source software news, a new tool called Banxaas is making Bitcoin more accessible in West Africa by integrating with local payment providers to facilitate buying and selling Bitcoin using the CFA currency (XOF). This on-and-off ramp could expand financial freedom for human rights activists, dissidents, and everyday citizens.
We end with the latest edition of the HRF x Pubkey Freedom Tech Series, in which HRF’s Zac Guignard sits down with author Jason Maier to discuss how Bitcoin can drive human rights around the world. Together, they examine the shortcomings of today’s financial system and discuss how Bitcoin is aiding people living under authoritarian regimes.
Now, let’s get right to it!
Subscribe Here
GLOBAL NEWS
Thailand | Announces Third Digital Cash Handout to Boost Economy
The government of Thailand announced a third digital cash handout, allocating 27 billion baht ($800 million) to 2.7 million citizens aged 16-20 to “stimulate the economy and drive technological adoption.” Like in previous phases, the regime will distribute the funds through a state-run “digital wallet” application, which would effectively function as a central bank digital currency (CBDC). Past handouts of the CBDC came with strict restrictions: spending was limited to approved vendors within designated areas, purchases were restricted to certain goods, and funds expired after six months. Meanwhile, Prime Minister Paetongtarn Shinawatra called this third handout the first full deployment of the digital wallet system and urged the public to download the official app. This would directly link citizens' financial activity and data to the regime, threaten privacy, and deepen repression in a country with a long history of silencing dissent.
Russia | Central Bank Proposes Restricting Bitcoin Access to Wealthy Only
Russia’s central bank has proposed restricting Bitcoin and cryptocurrency access to only the country’s wealthiest individuals, barring everyday Russians from buying and selling digital assets unless they meet specific income or asset thresholds. Under the proposal, only Russians with over $1.2 million in assets or an annual income above $580,000 could engage with digital assets — effectively putting Bitcoin officially out of reach of most activists and journalists. The central bank claims the measure protects citizens from “volatility and lack of state backing.” But in reality, it likely signals the regime’s fear of Bitcoin’s ability to provide individual financial autonomy. By blocking most Russians from opting out of the state-controlled financial system, the regime is doubling down on financial repression.
India | Advances Digital Rupee CBDC
India’s government is pushing forward with its CBDC, the Digital Rupee, hailing it as a modern payment solution. But as journalist and author Roger Huang puts it, “it looks like a solution searching for a problem to solve.” Beyond the branding, the Digital Rupee enables state control over financial activity. Its programmability allows the government to dictate how, when, and where people spend — restricting transactions to specific merchants, locations, or goods and even imposing expiration dates on money. India’s crackdown on dissent is well-documented, from freezing opposition bank accounts to attempting a Bitcoin ban. Now, the Reserve Bank of India is embedding the CBDC into its digital payment system (UPI), quietly pushing millions into a tightly controlled and surveilled financial system.
Zimbabwe | Financial Regulators Mandate Earnings in ZiG
Zimbabwe’s market regulator is mandating all companies report their earnings in the new ZiG currency despite it losing 96% of its value since its launch last year. This move tightens state control over an already fragile economy, pushing businesses and citizens deeper into an unstable system that has repeatedly wiped out savings through inflation. The ZiG is Zimbabwe’s sixth currency in 15 years, introduced with gold backing to restore confidence in the regime’s ability to manage a currency. Instead, it’s rapidly devaluing, while the US dollar remains the preferred currency for trade and savings — when accessible. For ordinary Zimbabweans, the mandatory use of ZiG for taxes and government services is already a challenge due to its scarcity.
Egypt | Dictator-imposed Reforms Causing Economic Chaos
In the wake of an $8 billion deal with the International Monetary Fund (IMF) last spring, the Egyptian dictatorship has carried out “reforms” that are fueling inflation and making necessities increasingly unaffordable. To meet IMF conditions, Egyptian officials devalued the pound, slashed subsidies, and hiked the cost of fuel and public transportation — driving inflation beyond 20% for months on end. For millions of Egyptians, basic goods are now unaffordable. And the government’s promised minimum wage increase for public workers remains unfulfilled, leaving the public to absorb the price shocks. These undemocratic reforms — never voted on and executed with no way for the public to push back — aimed at securing further financing have only eroded the financial freedom of 114 million Egyptians and pushed the country into greater debt.
China | Facebook Enabling Authoritarian Censorship
A former Meta executive, Sarah Wynn-Williams, has accused Facebook of working “hand in glove” with the Chinese Communist Party (CCP) to censor and surveil content in China. According to Wynn-Williams, Facebook explored building censorship tools that would suppress viral posts until Chinese authorities approved. They even considered sharing user data in exchange for market access to China’s massive user base. Meta denied these claims, saying they fired Wynn-Williams in 2017 for poor performance. Regardless, the revelations highlight the dangers of for-profit, centralized platforms that authoritarian regimes can co-opt. Protocols like nostr (where no single entity moderates content) are more important than ever. Activists and dissidents seeking free communications can get started with nostr here.
BITCOIN AND FREEDOM TECH NEWS
Banxaas | Spend Sats in West Africa
Hundreds of millions of citizens in West Africa still use the CFA franc in an arrangement upheld by more than a dozen authoritarian leaders. Banxaas offers an alternative by bridging Bitcoin with West Africa’s mobile money networks. This allows individuals to buy and sell Bitcoin through local payment providers using the local CFA currency (XOF) and their own Lightning wallet. By integrating with local payment providers, Banxaas serves as a crucial on-and-off-ramp to Bitcoin, bringing the benefits of financial freedom to individuals, nonprofits, and human rights defenders across the region. Watch a demonstration of how Banxaas works here.
Mi Primer Bitcoin | Bitcoin Workbook Translated to Mandarin
Mi Primer Bitcoin, an open-source Bitcoin educational initiative focused on high-school-age students, released a Mandarin translation of its 2025 Bitcoin Diploma. This open-source resource provides mainland Chinese citizens, activists, and dissidents with accessible Bitcoin education at a time when financial freedom is increasingly under threat. With China tightening restrictions on personal wealth and expanding state surveillance of financial activity through the digital yuan CBDC, the diploma offers a useful new resource to learn the alternatives to state-controlled financial systems.
Blitz Wallet | Improves Ecash Functionality for Greater Financial Autonomy
Blitz Wallet, an open-source and self-custodial Bitcoin Lightning, Liquid, and ecash wallet, released an update that improves ecash functionality. Ecash, a Bitcoin-backed digital money system, allows instant and private transactions but requires custodial “mints” to manage tokens. The new update links users’ ecash to their wallet’s seed phrase (the 12-word backup used for Bitcoin recovery), allowing them to restore funds even if their device is lost or stolen. Users can also now transfer ecash between different wallets, increasing flexibility and control over their funds. Improved ecash UX is much-desired for political dissidents who can’t afford for authoritarian regimes to have full oversight over all of their economic activities.
Fedimint | Adds On-chain Support for Everyone
Fedimint, an open-source Bitcoin custody model that lets communities securely manage Bitcoin funds together, released v0.6.0, adding support for on-chain Bitcoin deposits (transactions directly on Bitcoin’s base layer). By offering private and trust-minimized transactions alongside on-chain support, Fedimint makes it easier, especially for nonprofit communities, to self-custody Bitcoin. It provides greater privacy and autonomy versus using fully centralized platforms that are easily subject to the political and regulatory pressure of authoritarian regimes.
Africa Bitcoin Conference | Announces 2025 Conference
The Africa Bitcoin Conference (ABC) announced its fourth edition, set to take place from Dec. 3-5, 2025, in Port Louis, Mauritius. Hosted at the Caudan Art Center, the event will bring together activists, Bitcoin advocates, and freedom tech developers to explore Bitcoin as a pathway to financial freedom. Now the largest Bitcoin gathering in Africa, ABC has established itself as a key platform for discussions on financial inclusion, inflation resistance, and censorship-resistant money — putting tools for financial sovereignty into the hands of those who need them most. HRF is proud to support ABC and, in particular, is proud to help delegates from dozens of authoritarian regimes attend each year. You can learn more about the conference and buy tickets here.
RECOMMENDED CONTENT
HRF x Pubkey — How Bitcoin Brings About Social Change with Jason Maier
In the latest installment of the HRF x Pubkey Freedom Tech Series, HRF Content and Research Associate Zac Guignard sits down with Jason Maier, author of “A Progressive’s Case for Bitcoin,” to share how Bitcoin can spark a meaningful shift in personal liberty worldwide. Jason explains the core monetary properties that make Bitcoin permissionless, censorship-resistant, and a powerful tool for financial freedom. Together, they examine the shortcomings of today’s financial system and discuss how Bitcoin is aiding people living under authoritarian regimes. They talk about how Bitcoin shouldn’t be a political issue and can be useful to anyone, no matter their beliefs. Watch the full conversation here.
Mélancolies de l’Opprimé by Farida Bemba Nabourema
Farida Bemba Nabourema, a renowned Togolese human rights activist, former HRF freedom fellow, and Bitcoin pioneer, announced that her new book “Mélancolies de l’Opprimé” will be released on April 15, 2025. A decade after her first book, “La Pression de l’Oppression,” this deeply personal and reflective work offers hard-earned wisdom for young activists stepping into the struggle against dictatorships and injustice. Nabourema candidly shares the emotional, physical, and psychological toll of resistance and activism while also highlighting the sense of purpose in the pursuit of freedom and human rights. Learn more about the book here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 21335073:a244b1ad
2025-03-20 13:16:22
@ 21335073:a244b1ad
2025-03-20 13:16:22I’d never had the chance to watch Harry Potter on the big screen before. Experiencing the first movie in 3D was nothing short of spectacular. Right from the opening scene with Albus Dumbledore, I was floored—the makeup and costumes were so vivid, it felt like pure magic unfolding before my eyes. It’s clear that real masters of their craft worked behind the scenes, and their artistry shines through. The sets? Absolutely jaw-dropping! The level of detail in Diagon Alley was beyond impressive.
Seeing legends like Alan Rickman as Snape and Maggie Smith as Minerva McGonagall on that massive 3D screen was an unforgettable thrill. The film is packed with phenomenal actors, and it was a joy to catch every tiny eye twitch and subtle nuance of their performances brought to life. It was a mind-blowing experience, and I’d wholeheartedly recommend it to anyone who gets the chance.
Don’t forget to have a little whimsical fun sometimes my friends. 🪄
-
 @ 7d33ba57:1b82db35
2025-03-27 20:54:55
@ 7d33ba57:1b82db35
2025-03-27 20:54:55Andorra la Vella, the capital of Andorra, is a charming mix of mountain landscapes, duty-free shopping, and rich history. Nestled in the Pyrenees, it’s a great destination for skiing, hiking, and relaxing in thermal spas. Whether you’re here for outdoor adventures, tax-free shopping, or cultural experiences, Andorra la Vella has something for everyone.
🏔️ Top Things to See & Do in Andorra la Vella
1️⃣ Shop in Avinguda Meritxell 🛍️
- One of Europe’s best duty-free shopping streets, filled with electronics, fashion, perfumes, and luxury goods.
- Find brands at lower prices than in Spain or France.
2️⃣ Relax at Caldea Spa ♨️
- The largest thermal spa in Southern Europe, with hot springs, saunas, and lagoon pools.
- A perfect place to unwind after skiing or hiking.
3️⃣ Visit the Church of Sant Esteve ⛪
- A beautiful Romanesque church dating back to the 12th century.
- Features stone carvings and medieval frescoes.
4️⃣ Explore the Historic Quarter (Barri Antic) 🏡
- Walk through narrow cobbled streets filled with traditional Andorran houses and charming cafés.
- Visit Casa de la Vall, a historic parliament building from the 16th century.
5️⃣ Go Skiing or Snowboarding 🎿
- Andorra is famous for its world-class ski resorts, Grandvalira and Vallnord, just 15-30 minutes away.
- Ideal for beginners and experienced skiers alike.
6️⃣ Hiking in the Pyrenees 🥾
- Summer & autumn offer incredible hiking trails with mountain lakes and scenic views.
- Rec del Solà Trail – A beautiful, easy path with panoramic views of the valley.
- L’Estany Blau – A moderate hike leading to a stunning blue lake.
7️⃣ Enjoy Andorran Cuisine 🍽️
- Escudella – A hearty Andorran stew with meat, beans, and vegetables 🍲
- Trinxat – A mountain dish made of potatoes, cabbage, and bacon 🥓🥔
- Embotits – Local cured meats and sausages, perfect as tapas 🍖
- Crema Andorrana – A creamy, local dessert similar to Catalan crema 🍮
🚗 How to Get to Andorra la Vella
✈️ By Air: The nearest airports are Barcelona-El Prat (Spain, 2.5 hrs) and Toulouse-Blagnac (France, 2.5 hrs).
🚘 By Car: 2.5 hrs from Barcelona, 2.5 hrs from Toulouse, 3 hrs from Perpignan.
🚌 By Bus: Direct buses from Barcelona, Toulouse, and Lleida.
🚆 By Train: No direct train, but you can take a train to L'Hospitalet-près-l'Andorre (France) and continue by bus.
💡 Tips for Visiting Andorra la Vella
✅ Best time to visit? Winter for skiing, summer for hiking & shopping ❄️🌞
✅ Bring a passport – Even though Andorra isn’t in the EU, border checks happen 🇦🇩
✅ Try duty-free shopping – Electronics, perfumes, and alcohol are cheaper 🛍️
✅ Book ski passes in advance – Resorts get busy in peak season 🎿
✅ Wear comfy shoes – The city has steep streets and cobblestone paths 👟 -
 @ a60e79e0:1e0e6813
2025-03-20 12:58:13
@ a60e79e0:1e0e6813
2025-03-20 12:58:13*This is a long form Nostr native version of a post that lives on my Nostr educational website Hello Nostr *
At first glance Nostr might appear quite similar to some of the apps you use every day, such as Twitter, Mastodon, or Facebook, but that couldn't be further from the truth. This post aims to dispel the myth that "Nostr is just a Twitter replacement" and give you a better understanding about the 'what', the 'how' and most importantly, the 'why' of Nostr.
What Is Nostr?
Nostr is a decentralized, open-source protocol designed for censorship-resistant networking and communication on the web. It stands for "Notes and Other Stuff Transmitted by Relays," and it works by allowing users to publish messages (notes) and content in the form of 'other stuff', to a network of servers (relays) that store and distribute the content.
Unlike traditional platforms like Twitter, Ebay or Facebook, Nostr doesn't rely on a central authority; instead, users control their own identities via cryptographic key pairs.
The simplest open protocol that is able to create a censorship-resistant global "social" network once and for all.
Fiatjaf - Nostr Creator
Nostr is not a website or an app you download from a single source — it’s an open protocol, like email or the internet. Think of it as a set of rules that anyone can use to build tools for sharing messages, posts, or other data without needing a centralized middleman like a big tech company.
Nostr was created by a developer named Fiatjaf in 2020, and has since been steadily gaining traction among people who care about privacy, freedom, and censorship resistance.

Why Nostr?
Imagine the scenario, you've been using an online platform for 5 or even 10 years. You've built up thousands of contacts, perhaps built yourself a sizeable reputation, or even rely on the income from the platform to feed your family. Then one day you make a controversial post, sell a certain item or upload a video on a spicy subject to the platform where the owner disagrees with. With the click of a button, your account is removed. All trace of you, your social graph, or even your future income, disappears in an instant.
Read aloud like that is sounds crazy that we'd even entertain using such a platform, right!? Sadly that is the reality in 2025. This is exactly what happens every single day on X, Facebook, Ebay, Paypal, Linkedin, etc.
Looking at the problem through a more social media focused lens, many of us have become slaves to the likes of Instagram, Twitter and TikTok. We use these 'free' apps under the guise of being social with others online. The reality is that we see what those apps want us to see. We've become slaves to the manipulation of complex and opaque algrorithms designed to keep us hooked and try to sell us things.

Unlike traditional platforms, which are often governed by centralized entities wielding significant control over user data, content moderation, and algorithmic influence, Nostr flips the script by prioritizing user sovereignty and resilience. Built on an open-source framework, Nostr allows individuals to control their own data and interact through a network of relays, making it much more difficult for any single authority - be it a corporation, government, or bad actor - to censor or manipulate the flow of information.
- Is a relay refusing to host your notes? Use another or run your own!
- A specific client using an algorithm you don't like, take your identity and social graph elsewhere and choose another!
Take your identity and social graph with you, anywhere any time.
Nostr’s ability to foster authentic, unfiltered conversations while safeguarding user sovereignty has made it a cornerstone for communities seeking alternatives - whether they’re activists, creators, or everyday people tired of being pawns in the data-driven game. It's simple and adaptable design also encourages innovation, inviting developers to build tools and interfaces that keep pushing the boundaries of what the decentralized internet can achieve. In short, Nostr isn’t just a tool; it’s a movement toward a freer, more equitable digital future.

How Does Nostr Work?
Instead of one giant server owned by a single company holding all your posts and messages, Nostr spreads everything across lots of smaller servers called relays. To get started, you download a client, create your account and back up your private key. Your private key is used to secure your account and sign every message you send over the network. This allows anyone you interact with the verify the integrity of the data coming from 'you'.
The Nostr network is essentially a collection of bulletin boards that share a common format
When you write a note, or share some other type of compatible data, your client signs it with your private key, then sends it to one or more relays. Which relays your information is sent to is entirely up to you. These relays share your message with others who want to see it.
For others to see your notes or 'other stuff', they'll need to be able to find you. Typically this is done by using your public key, which looks something like this
npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx. Don't panic though, you don't need to memorize all of your friends public keys, there are more human friendly methods of finding people that we'll come onto later.Once someone is following you, their client will ask all of their connected relays for any data shared by your public key. Their client will receive this data, verify it is signed by your private key and then populate it into their feed.
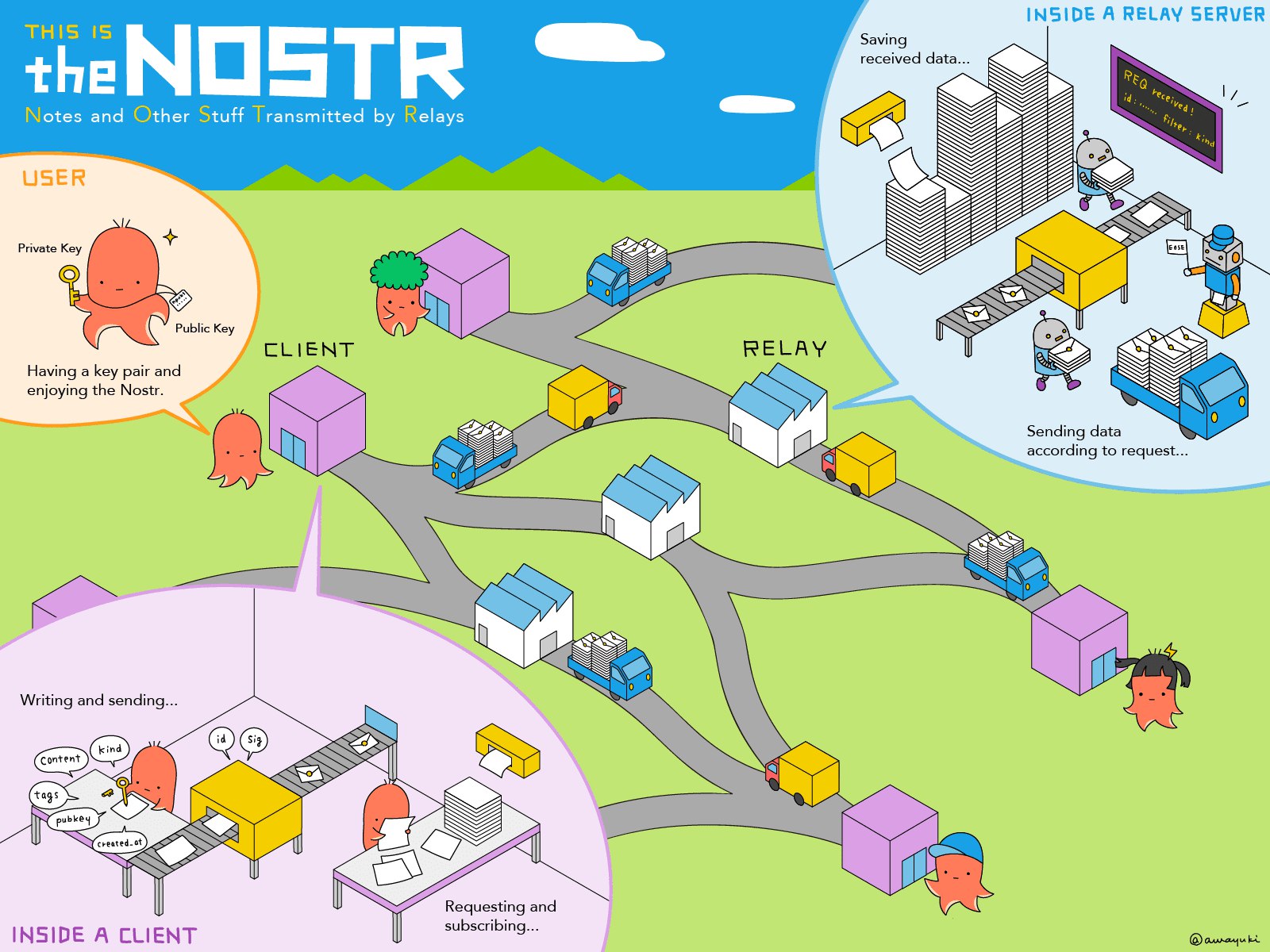
The “Other Stuff” Explained
Nostr’s name hints at this: Notes and Other Stuff Transmitted by Relays. But what is the “other stuff”? Put simply, it’s all the creative and experimental things people are building on Nostr, beyond simple text based notes. Every action on Nostr is an event - like a post, a profile update, or even a payment. The 'Kind' is what specifies the purpose of each event. Kinds are the building blocks of how information is categorized and processed on the network, and the most popular become part of higher lever specification guidelines known as Nostr Implementation Possibility - NIP. A NIP is a document that defines how something in Nostr should work, including the rules, standards, or features. NIPs define the type of 'other stuff' that be published and displayed by different styles of client for different purposes.
Here's some content examples of 'Other Stuff':
- Long-Form Content: Think blog posts or articles. NIP-23.
- Private Messaging: Encrypted chats between users. NIP-04.
- Communities: Group chats or forums like Reddit. NIP-72
- Marketplaces: People listing stuff for sale, payable with zaps. NIP-15
- Zaps: Value transfer over the Lightning Network. NIP57
The beauty of Nostr is that it’s a flexible foundation. Developers can dream up new ideas and build them into clients, and the relays just keep humming along, passing the data around. It’s still early days, so expect the “other stuff” to grow wilder and weirder over time!
Clients vs Relays: What’s the Difference?
Newbies often get tripped up by these two terms, so let’s clearly define them.
Clients
A client is what you use to interact with Nostr. It’s the app or website where you type your posts, read your feed, follow and interact with others. Examples of Nostr clients include:
- Damus (iOS Twitter style client)
- Primal (Cross-platform Twitter style client)
- Amethyst (Android only Twitter style client)
- Habla.News (Web based blog client)
- Olas (Instagram style client)
- 0xchat (Messaging client)
Clients don’t store your data; they just pull it from relays and display it for you. You can switch clients whenever you want, and your account stays the same because it’s tied to your keys, not any single client or app.
Clients are how you use Nostr, and relays are where the data lives. You need both to make the magic happen.
Relays
A relay is a server that stores and shares Nostr data. It’s a little like a post office: you send your note to a relay, and it delivers it to anyone who’s subscribed to see it (like your followers). Relays are run by individuals, groups, or companies who volunteer their computing power. Some are free, some charge a small fee, and you can connect to as many as you like. Most clients will come pre-configured with a list of well-known relays, but you can add or remove any you like.
What Are Zaps?
Zaps are arguably one of Nostr’s coolest features! A zaps is a way to send payments in Bitcoin directly to other users. Imagine liking a post, but instead of just clicking a heart (which you can of course do), you send the poster a few cents worth of Bitcoin to say, “This is awesome!”.
Zaps use Bitcoin's Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider.
Zaps are optional but add a fun layer to Nostr. Creators love them because it’s a way to get direct support from fans, with no middleman required.
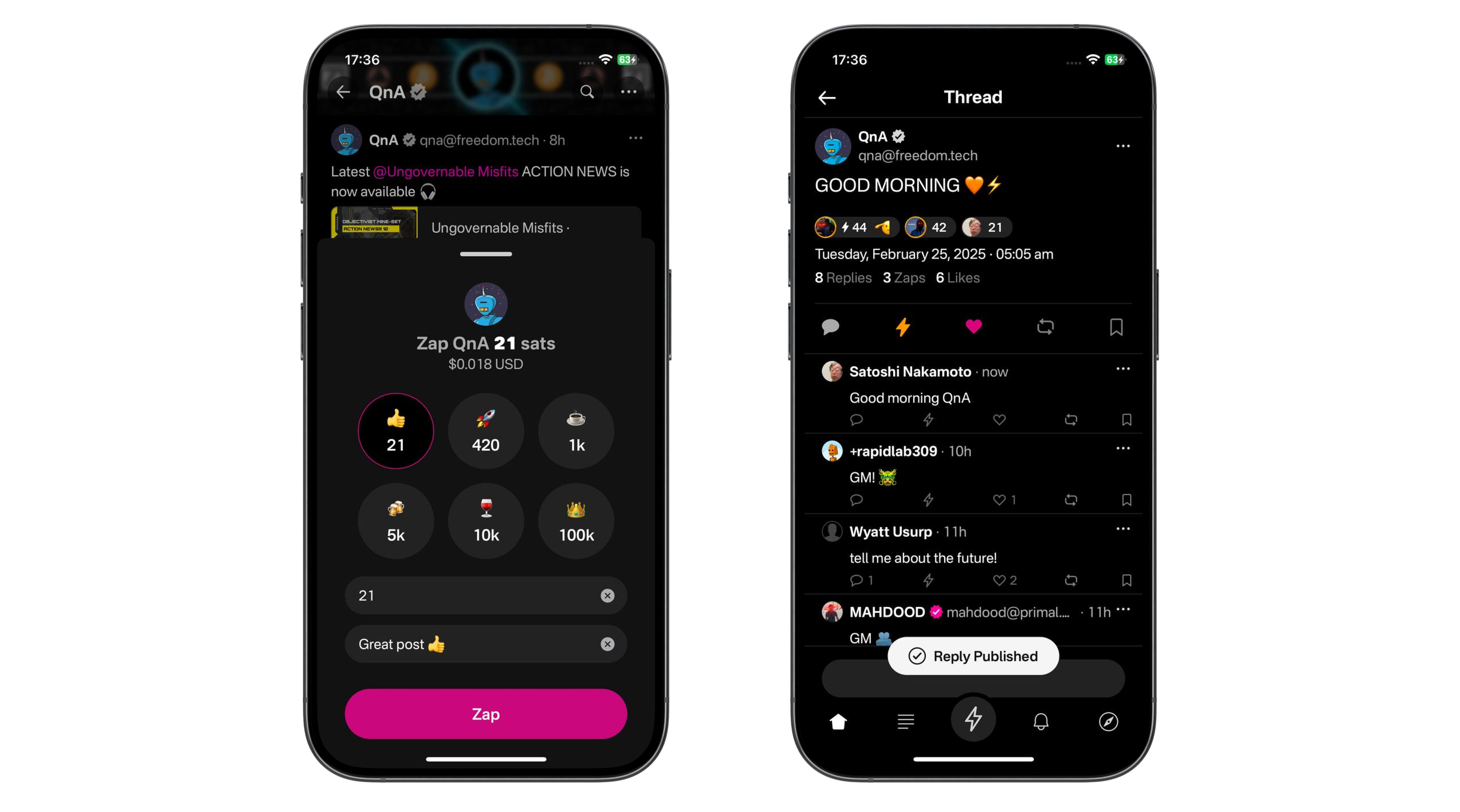
NIP-05 Identifiers: Your Nostr “Username”
Your nPub, or public key (that long string of letters and numbers) is your 'official' Nostr ID, but it’s not exactly catchy. Enter NIP-05 identifiers, a human-readable and easily sharable way to have people find you. They look like an email address, like
qna@hellonostr.xyz.Here’s how it works:
Most users obtain their NIP-05 ID from a website or service that supports Nostr. Some of these services are free whereas some charge a fee. Some clients, like Primal will set one up for you automatically when you create an account. The email like ID links to your public key, so people can find you more easily. And because these ID's are domain based, there can be no duplicates. qna@hellonostr.xyz can only map to a single public key. The only person that can change that link is the person in control of the domain.
If you control your own domain, you can easily map your Nostr public key to name@my.domain. It’s not mandatory, but it’s super useful for building trust and making your profile recognizable.
Next Steps
So you're bought in. You understand why Nostr is so important and want to get started. Check out our simple onboarding guide here.
Thanks For Reading
Hopefully that moistened your taste buds for more educational Nostr content. This was a basic one, but there will be more focused material coming soon.
If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I'll be sure to Zap you back! ⚡️
-
 @ 20e17dd0:2ae504d7
2025-03-20 10:04:35
@ 20e17dd0:2ae504d7
2025-03-20 10:04:35Prerequisite
Installation
Open a Terminal session and write the following command to make sure that Docker is running:
ruby sudo systemctl status dockerYou should get a screen with the docker.service as "running". To get back to command line do CTRL+C
Then, create the volume that Portainer Server will use to store its database:
ruby sudo docker volume create portainer_dataYou are now ready for the on-liner installation:
ruby sudo docker run -d -p 8000:8000 -p 9443:9443 --name portainer --restart=always -v /var/run/docker.sock:/var/run/docker.sock -v portainer_data:/data portainer/portainer-ce:latestTo validate the installer, prompt the following command:
ruby sudo docker psYou should see Portainer's container running.
To access Portainer Server, go to the following adress: https://localhost:9443
Et voila!
-
 @ 7d33ba57:1b82db35
2025-03-27 20:23:58
@ 7d33ba57:1b82db35
2025-03-27 20:23:58Peñíscola, known as the “Gibraltar of Valencia”, is a stunning coastal town on Spain’s Costa del Azahar. Famous for its medieval castle, beautiful beaches, and charming old town, Peñíscola is a perfect mix of history, culture, and seaside relaxation. It’s also known as a filming location for Game of Thrones!
🏖️ Top Things to See & Do in Peñíscola
1️⃣ Peñíscola Castle (Castillo del Papa Luna) 🏰
- A magnificent 13th-century castle sitting on a rocky peninsula.
- Built by the Knights Templar and later home to Pope Benedict XIII (Papa Luna).
- Offers breathtaking views of the Mediterranean and surrounding coastline.
2️⃣ Explore the Old Town 🏡
- Wander through narrow cobblestone streets, lined with whitewashed houses and flower-filled balconies.
- Discover hidden courtyards, charming shops, and seafood restaurants.
- Enjoy the picturesque sunset views over the sea.
3️⃣ Relax on Playa Norte & Playa Sur 🏖️
- Playa Norte: The main beach, known for its golden sand and clear waters.
- Playa Sur: Smaller and quieter, great for relaxing away from the crowds.
- Both beaches offer water sports, sunbeds, and beach bars.
4️⃣ Serra d’Irta Natural Park 🌿
- A stunning coastal nature reserve with hiking and biking trails.
- Offers hidden coves, rugged cliffs, and breathtaking sea views.
- Ideal for nature lovers and photographers.
5️⃣ Game of Thrones Filming Locations 🎬
- Peñíscola was featured in Game of Thrones (Season 6) as Meereen.
- Visit the castle walls, old town alleys, and city gates where key scenes were filmed.
6️⃣ Boat Trip Around the Castle ⛵
- Take a boat tour for unique views of the fortress from the sea.
- Sunset cruises offer magical golden-hour scenery.
🍽️ What to Eat in Peñíscola
- Arroz a Banda – A delicious seafood rice dish, typical of Valencia 🍚🐟
- Suquet de Peix – A traditional fish stew with potatoes and saffron 🍲
- Langostinos de Vinaròs – Famous local prawns, incredibly fresh 🍤
- Caragols Punxents – A local specialty of small spicy snails 🐌🌶️
- Coca de llanda – A sweet sponge cake, perfect with coffee 🍰
🚗 How to Get to Peñíscola
✈️ By Air: The nearest airport is Castellón Airport (40 min), Valencia (1.5 hrs), or Barcelona (2 hrs).
🚆 By Train: The nearest station is Benicarló-Peñíscola, just 7 km away.
🚘 By Car: 1.5 hrs from Valencia, 2 hrs from Barcelona, 45 min from Castellón.
🚌 By Bus: Direct buses from Barcelona, Valencia, and Castellón.💡 Tips for Visiting Peñíscola
✅ Best time to visit? Spring & summer (April–September) for the best weather ☀️
✅ Visit the castle early – Mornings are less crowded and cooler 🏰
✅ Take a sunset walk along the beach – The views are stunning 🌅
✅ Try a boat trip – The castle looks incredible from the water ⛵
✅ Wear comfortable shoes – The old town streets are steep and cobbled 👟 -
 @ 8fb140b4:f948000c
2025-03-20 01:29:06
@ 8fb140b4:f948000c
2025-03-20 01:29:06As many of you know, https://nostr.build has recently launched a new compatibility layer for the Blossom protocol blossom.band. You can find all the details about what it supports and its limitations by visiting the URL.
I wanted to cover some of the technical details about how it works here. One key difference you may notice is that the service acts as a linker, redirecting requests for the media hash to the actual source of the media—specifically, the nostr.build URL. This allows us to maintain a unified CDN cache and ensure that your media is served as quickly as possible.
Another difference is that each uploaded media/blob is served under its own subdomain (e.g.,
npub1[...].blossom.band), ensuring that your association with the blob is controlled by you. If you decide to delete the media for any reason, we ensure that the link is broken, even if someone else has duplicated it using the same hash.To comply with the Blossom protocol, we also link the same hash under the main (apex) domain (blossom.band) and collect all associations under it. This ensures that Blossom clients can fetch media based on users’ Blossom server settings. If you are the sole owner of the hash and there are no duplicates, deleting the media removes the link from the main domain as well.
Lastly, in line with our mission to protect users’ privacy, we reject any media that contains private metadata (such as GPS coordinates, user comments, or camera serial numbers) or strip it if you use the
/media/endpoint for upload.As always, your feedback is welcome and appreciated. Thank you!
-
 @ 7d33ba57:1b82db35
2025-03-27 19:48:38
@ 7d33ba57:1b82db35
2025-03-27 19:48:38Tarifa, located at the southernmost tip of Spain, is a paradise for beach lovers, adventure seekers, and nature enthusiasts. Known for its strong winds, golden beaches, and laid-back atmosphere, it’s a top destination for kite surfing, whale watching, and exploring Andalusian history. Plus, it’s the perfect gateway to Morocco, just a short ferry ride away.

🏖️ Top Things to See & Do in Tarifa
1️⃣ Playa de Los Lances 🏄♂️
- A long, sandy beach famous for kite surfing and windsurfing.
- One of the best spots in Europe for water sports enthusiasts.
- Lined with chiringuitos (beach bars) where you can relax and enjoy the views.
2️⃣ Punta de Tarifa – The Southernmost Point of Europe 🌍
- A unique spot where the Atlantic Ocean meets the Mediterranean Sea.
- Walk to Isla de las Palomas, a historic military zone (guided tours available).
- Incredible views of Morocco, just 14 km away.

3️⃣ Whale & Dolphin Watching Tours 🐬
- Join a boat trip to see orcas, dolphins, and sperm whales in the Strait of Gibraltar.
- Best time: April to October for whale migrations.
4️⃣ Explore the Historic Old Town 🏰
- Wander through narrow, whitewashed streets full of charm.
- Visit Guzmán el Bueno Castle, a 10th-century fortress with panoramic views.
- Enjoy lively tapas bars, boutique shops, and hidden courtyards.
5️⃣ Playa de Bolonia & Baelo Claudia Ruins 🏛️
- One of Spain’s most unspoiled beaches, with dunes and turquoise waters.
- Explore the Roman ruins of Baelo Claudia, an ancient fishing village from 2,000 years ago.
- Climb the Duna de Bolonia, a massive sand dune with breathtaking views.
6️⃣ Day Trip to Morocco 🇲🇦
- Take a 35-minute ferry to Tangier for a quick taste of North African culture.
- Explore medinas, souks, and local cuisine with a guided tour.
- Don’t forget your passport!

🍽️ What to Eat in Tarifa
- Atún Rojo (Red Tuna) – Tarifa is famous for its fresh bluefin tuna 🍣
- Tortillitas de Camarones – Crispy shrimp fritters, a local delicacy 🍤
- Choco Frito – Fried cuttlefish, a must-try for seafood lovers 🦑
- Andalusian Gazpacho – A refreshing cold tomato soup, perfect for hot days 🍅
- Mojama – Salt-cured tuna, often eaten as a tapa with almonds 🐟
🚗 How to Get to Tarifa
✈️ By Air: The nearest airports are Gibraltar (45 min), Málaga (2 hrs), and Seville (2.5 hrs).
🚆 By Train: No direct train, but you can take one to Algeciras (30 min drive from Tarifa).
🚘 By Car: 1.5 hrs from Málaga, 1 hr from Cádiz, 30 min from Gibraltar.
🚌 By Bus: Regular buses from Seville, Málaga, Cádiz, and Algeciras.
⛴️ To Morocco: Ferries run daily to Tangier, Morocco (35 min ride).
💡 Tips for Visiting Tarifa
✅ Best time to visit? Spring to early autumn (April–October) for great weather ☀️
✅ Book water sports lessons early – It’s a popular spot for kite surfing! 🏄♂️
✅ Bring layers – Tarifa can be windy, even in summer 🌬️
✅ Visit early for whale watching – Mornings usually have calmer seas 🐋
✅ Take a day trip to Bolonia – One of Spain’s most stunning hidden beaches 🏝️
-
 @ fe9e99a0:5123e9a8
2025-03-27 18:37:28
@ fe9e99a0:5123e9a8
2025-03-27 18:37:28Can’t seem to update anything
-
 @ 30ceb64e:7f08bdf5
2025-03-19 21:29:59
@ 30ceb64e:7f08bdf5
2025-03-19 21:29:59NIP-101e: Workout Data and Running Extensions
NIP-101e represents a crucial step forward for fitness tracking on Nostr, giving us a common language that would allow workout data to flow freely between apps. This proposal outlines a thoughtful framework with Exercise Templates, Workout Templates, and Workout Records that would finally free our fitness data from proprietary silos and put it back in our hands. I'm eager to see this proposal implemented because it would create the foundation for a genuinely open fitness ecosystem on Nostr.
As a runner building a Nostr running app RUNSTR, I've proposed some running-specific extensions to NIP-101e that address the unique needs of runners without disrupting the elegant structure of the original proposal. My extensions would standardize how we record GPS routes, pace metrics, elevation data, splits, and even weather conditions - all things that matter tremendously to runners but aren't covered in the base proposal that focuses more on strength training.
By implementing NIP-101e along with these running extensions, we could create something truly revolutionary: a fitness ecosystem where runners aren't locked into a single platform because of their data. You could track your morning run in my app, analyze your training in another app that specializes in statistics, and share achievements with friends using whatever Nostr clients they prefer. I believe strongly in getting NIP-101e implemented with these extensions included because it would foster innovation while giving runners unprecedented freedom to own their data and use it however they want. Let's make this happen and show what's possible when fitness data becomes truly interoperable!
-
 @ a296b972:e5a7a2e8
2025-03-27 17:05:57
@ a296b972:e5a7a2e8
2025-03-27 17:05:57Wehrpflicht, Wehr-Pflicht… Da soll die allgemeine Wehrpflicht wieder eingeführt werden. Eine Frage taucht auf: Ist sie denn jemals abgeschafft worden? Ist die Wehrpflicht nicht untrennbar mit der Demokratie verbunden? Ist es nicht die Pflicht eines jeden Demokraten, sich zu wehren, wenn er sieht, wie die Demokratie vor die Hunde geht? Muss er sich nicht wehren, wenn er feststellt, dass die Freiheit scheibchenweise immer weniger wird?
In Absurd-Germanistan reizt ein wild gewordener Haufen Irrer in Berlin die Grenzen der Legalität bis zum Äußersten aus. Unterstützt von Erfüllungsgehilfen in der Rechtsprechung und den Medien. Neuester Coup: Zur größtmöglichen Intransparenz soll das Informationsfreiheitsgesetz abgeschafft werden. Unterstützt von einer eigenen Bundestagspolizei, geschützt von einem Wassergraben um den Reichstag. Die dunkle Seite der Macht baut eine Beton-Mauer auf, um größtmöglichen Abstand zum übelriechenden Volk, dass sie gewählt hat, zu gewährleisten. Und mit ekelhafter Regelmäßigkeit werden Knochen mit Fleischresten über die Mauer geworfen, die dann das dumme Volk zu verdauen hat. Das funktioniert derzeit noch, weil das Volk nicht in der Lage ist, eine Leiter an die Mauer zu stellen, um die Irren über die Mauer in den Wassergraben zu werfen und sich das saftige Hühnchen zu holen, das ihm, dem Volk sowieso gehört.
Unterdessen sinniert die entrückte Blase darüber, wie man dem Volk nachhaltig langfristigen Schaden zufügen kann. Aus rechtlichen Winkelzügen, falschen Versprechungen, Selbstbeweihräucherungen, ideologisch vergifteten Reden quillt die Verachtung gegenüber dem Volk und der Demokratie aus allen Poren. Und die wird dann durch Unseredemokratie verhöhnt, in der Schulden durch eine Wortneuschöpfung als Sondervermögen ausgegeben werden. Dreister und offensichtlicher kann man nicht lügen. Und das mit einer nie gekannten Chuzpe, dass einem nur noch der Atem stockt.
Jahrzehnte wurde den Deutschen abgewöhnt, stolz auf ihr Land zu sein. Die deutsche Fahne zeigen, hatte damals schon den Charme von „reeechts“. Wer von Vaterland und Heimat sprach, der bekam automatisch einen dunklen, schmalen Schatten zwischen Nasenmitte und Mund. Doch dann, als es mal wieder Spiele für’s Volk gab, durfte man auf einmal mit kleinen Wink-Elementen zeigen, dass man stolz auf elf Leute war, die hinter einem Ball herrennen und wenn sie ihn hatten, ihn dann wieder wegschossen. Damit nicht genug, es gab hochalberne Gamaschen für Außenspiegel und Diplomatenfähnchen in schwarz-rot-gold für des Deutschen liebstes Kind, das Auto.
Und jüngst kam einer daher, der wie von der Tarantel gestochen behauptete, dass der böse Russ hinter uns her ist, und man deshalb kriegstüchtig werden müsse, obwohl weit und breit nichts von ihm zu sehen war und er immer wieder wiederholte, dass er überhaupt gar keine Lust dazu hat, Deutschland auf unschöne Weise bereisen zu wollen.
Im Fieberwahn stimmten weitere Kriegstreiber in den Chor ein und ein deutscher Häuptling der Bleichgesichter, der ehedem Streubomben geächtet hatte, zuckte auf einmal nur verbal mit den Schultern. Das soll einer verstehen.
Und weil Deutschland von nichts und niemandem bedroht wird, muss deshalb dringend aufgerüstet werden, Kriegswirtschaft ist angesagt, die Wehrpflicht muss wieder her!
Eine Kriegsmaschinerie muss von Grund auf neu aufgebaut werden: Von der langen Feinripp-Unterhose mit Eingriff bis zum Panzer. Die ehemaligen Hermann-Göring-Werke müssen die Fließbänder zum Glühen bringen. Wir brauchen „Woffen, Woffen, Woffen“!
Das Ganze dauert 10 bis 20 Jahre. Hoffentlich reicht der im Samowar zubereitete Tee so lange, bis alles zertifiziert und DIN-Norm gerecht fertiggestellt ist. Man kann nur auf die christlich demokratische Unterstützung der nach einer europäischen Zentralregierung strebenden, deutschen Ex-Verteidigungsministerin mit Ambitionen zur Kaiserin von Europa hoffen. Ihre Expertise konnte sie ja dank ihres mit Bravour gemeisterten ehemaligen Amtes bereits unter Beweis stellen. Überhaupt, überall, wo das Militär im Hintergrund seine Finger im Spiel hat, ist die Wahl-Brüsselerin an vorderster Front. Zuletzt im Beschaffungswesen der 1. Pandemie-Spiele in Echtzeit unter realen Bedingungen.
Aber was nutzt das ganze schöne Zeug, die noch nicht bekleckerten jungfräulichen Gulasch-Kanonen, wenn sie keiner bedient und keiner seinen Henkelmann mit Feinkost füllen will.
Ja genau, es fehlen ja noch Menschen, in dem Metier Soldaten genannt.
Ein paar Natur-Wahnsinnige gibt es ja immer. Aber was ist mit denen, die vielleicht gar keinen Bock haben? Gerade frisch verliebt, von Papi das erste Auto vor die Tür gestellt bekommen, wegen Laktose-Intoleranz bitte nur einen Kriegs-Latte mit Hafermilch, und für mich bitte glutenfreie Marschverpflegung.
Was ist mit denen, die vielleicht checken, dass wir von einer Polit-Klicke regiert werden, die Deutschland an die Wand fährt und sich redlich Mühe gibt, eine positive Zukunft für die nächsten Generationen zu verunmöglichen?
Was ist mit denen, die von Anfang an gerafft haben, dass man mit einer Gen-Behandlung die Wehrkraft zersetzt?
Was ist mit denen, die die Pflicht, sich bestmöglich gesund zu halten, ernst genommen haben?
Was ist mit denen, die aus Sachzwängen oder Unwissenheit die Injektionen über sich haben ergehen lassen und heute feststellen, dass man sie verarscht hat?
Was ist mit denen, die sich an ihrem durchtrainierten Six-Pack nur noch durch Bilder erinnern können, weil sie seit der Verabreichung eines „nebenwirkungsfreien Elixiers“ nicht mehr auf die Beine kommen?
Man fragt sich, woher soll die Motivation kommen, sein gesundes oder herabgemindertes Immunsystem für ein Vaterland auf’s Spiel zu setzen, bei dem sich herausgestellt hat, dass der Vater ein Stiefvater der übelsten Sorte ist?
Da in Europa offensichtlich die Diplomatie zunächst abgeschafft ist, und demnächst vielleicht sogar unter Strafe gestellt wird, und man sich auf Uncle Sam auch nicht mehr verlassen kann, weil er so völlig das Gegenteil von dem unternimmt, was man von ihm erwartet hätte, wäre es überlegenswert, ob diejenigen jungen Männer im fortpflanzungsfähigen und -willigen Alter eventuell eine längere Reise ins Ausland antreten sollten. Ist nur so ein Gedanke.
Man kann ja immer noch mal wieder vorbeischauen, wenn es an den ungeschützten Außengrenzen wieder von Deutschland aus nach Vernunft duftet.
Aber vielleicht findet sich auch unter den Messerfachkräften der eine oder andere, der seine Künste und sein Leben für ein Land und Bürgergeld hergeben möchte. Schließlich können es die Allermeisten kaum abwarten, die deutschen Gepflogenheiten ungefiltert einzusaugen und dafür ihre kulturelle Herkunft und Religion wie einen alten Lumpen abzuwerfen. Was Besseres, als die Kultur der Denker und Dichter hat die Welt ohnehin noch nicht gesehen. Wer kann dem schon widerstehen?
Großer Dank gilt auch der deutschen Bevölkerung, die einem wildgewordenen andalusischen Stier gleich, in Scharen von einigen Tausenden von über 80 Millionen auf die Straße rennen, um ihrem Unbill Ausdruck zu verleihen. So eine Friedensmüdigkeit ist ansteckend und kann richtig mobilisieren. Man kann natürlich auch was von Zuhause aus tun: Sich laut empören und für durchziehende Truppen Kaffee kochen, oder dem Heimatschutz beim Stiefel putzen helfen. Im Ernst: So eine bräsige, behäbige, langweilige, unmotivierte, unkritische, informationsvergiftete, geduldige Herde von Faultieren hat es eigentlich nicht anders verdient, als dass man sie während ihres andauernden Langzeit-Wachkomas in einen Käfig sperrt und mit Bananen füttert.
Keiner, niemand kommt auf die Idee, dass es immer noch besser wäre, obwohl es keinerlei Anlass dazu gibt, russisch zu lernen, als sich als Kanonenfutter für einen Staat, der sein Volk verachtet, in die Gefahr zu begeben, im Ernstfall verstümmelt oder abgeschlachtet zu werden.
Man kann jetzt schon die heulenden Bubis sehen, wie sie sich unter Mutterns Rockschürze verkriechen, wenn sie merken würden, dass es in den Ballerspielen am Computer aber immer ganz anders war.
Der ganze inszenierte Spuk wäre sofort vorbei, wenn die Menschen ihr Gehirn einschalten würden. Dann würden sie feststellen, dass es unzählige Gründe dafür gibt NEIN zu sagen und ICH MACH DA NICHT MIT.
Wie machtlos wären die Kriegspfeifen in Berlin, wenn sie zu spüren bekämen, dass das deutsche Volk nicht mit Russland oder sonst wem im Krieg ist und nicht das geringste Interesse verspürt, daran etwas zu ändern. Deutschland besteht aus einem erbärmlichen Haufen Ja-Sagern in allen Lagern, die offensichtlich erst dann wach werden, wenn es nichts mehr zu Essen gibt und der Strom fürs externe Gehirn weg ist. Oh Gott, mein Leben hat keinen Sinn mehr! Was sind wir doch ein elender Haufen von Jammerlappen, die glauben, dass man gelebte Demokratie und Freiheit jederzeit im Online-Shop kaufen kann. Lieferung innerhalb 24 Stunden.
Frieden – Mir – Pace – Peace
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ ed84ce10:cccf4c2a
2025-03-27 14:55:40
@ ed84ce10:cccf4c2a
2025-03-27 14:55:40Hackers are Destiny: Four Fulcrums of the Future
A Dora Ventures Thesis
In “Why Software is Eating the World,” Marc Andreeson argued that software isn’t just a tool — it’s a societal force. At DoraHacks, we agree, but we go one step further.
It’s not software alone that reshapes the world. It’s hackers — those who BUIDL.
The real engine of change isn’t technology; it’s the people who choose to wield it.
DoraHacks is building a global Hacker Movement — a self-organizing force powered by open source, freedom, and code. We’re not chasing buzzwords like “Web3” or geopolitical narratives. We’re building a new society. One based on a simple but radical question:
What is truly worth building?
Dora Ventures exists to serve that mission — a capital engine designed to coordinate, amplify, and capture value from the hacker revolution.
We are placing early and aggressive bets across four core leverage points:
I. FDA Free Society — The BioHack
Freedom of Life Science is the foundation of a free society.
Every meaningful technological revolution has challenged the existing power structure.
Today, the single most over-regulated, over-centralized, and innovation-hostile domain? Life Science.
It takes ten years and billions of dollars to bring a drug from lab to patient. Most innovation dies in the trenches of bureaucracy.
We don’t need anarchy. We need a new model:A market-driven, patient-first biotech innovation stack.
The Problem:
- The FDA approval process kills breakthrough therapies before they live.
- Big Pharma monopolies decouple price from value and destroy competition.
- The “Right to Try” is a legal afterthought, not a first principle.
- Bio startups can’t survive the upfront costs of traditional trials.
The Opportunity:
- Let markets and builders lead: give power back to patients, doctors, and founders.
- Rethink from first principles: not “Did it pass?” but “Does it work?”
- Reclaim the Right to Try: the real risk is dying while waiting.
- Build a hyper-competitive biofounder ecosystem — don’t just supply Big Pharma with IP.
- Supercharge biotech with software and AI: accelerate every layer of the stack.
The future of medicine does not belong to regulators. It belongs to the builders who refuse to wait.
The FDA Free Society isn’t just a challenge to power — it’s a defense of life.
II. Open Source Quantum
Ethereum had 2015. Quantum software has 2025.
Arthur C. Clarke said: “Any sufficiently advanced technology is indistinguishable from magic.”
Quantum is magic — until it’s programmable, repeatable, and shared. In other words: open source.
Dora Ventures is betting on the moment quantum computing becomes a hacker’s playground.
Hardware is entering the engineering phase. Software? Still a wasteland — which means pure upside for builders.
We’re betting on:
- Quantum compilers & transpilers: bridging classical and quantum logic.
- Quantum cryptography: building fundamentally new security layers.
- Quantum applications in AI, pharma, logistics, finance, space — everything.
We're not watching from the sidelines. We’re funding open-source tools, running hackathons, and building out the decentralized quantum dev stack.
Open Source Quantum is not speculative. It’s inevitable — and massively undercapitalized.
Now is the time to build.
III. Consumer Crypto — The Fat Apps Are Coming
Crypto’s real revolution? Billion-user apps.
Crypto is not the alternative to the internet. It’s the next chapter of the internet.
In the 1990s, HTTP and TCP/IP rewired information.
In the 2000s, web apps rewired commerce and communication.
In the 2010s, mobile apps rewired human behavior.
In the 2020s, crypto apps will onboard the next billion users.
The infrastructure is ready. The fat apps are hatching.
Dora Ventures is obsessed with one question:
Who builds the PayPal and WeChat of the Web3 era?
That’s where we place our bets.
What we see coming:
- Compliant stablecoins like USDC become digital dollars.
- Crypto-native payment rails rival VISA.
- Appchains built with Move + simplified UX onboard non-crypto users.
- On-chain creator economies that pay artists, devs, and communities directly.
Imagine this:
A fan in NYC uses USDC on a Move-based blockchain (Aptos) to buy a concert ticket via KYD Labs.
An Argentinian grabs a latte daily with Bitcoin sats on Lightning.
A friend group splits dinner bills via Yakihonne, a decentralized social platform.
That’s not the future. That’s this year.
We’re not funding protocols — we’re funding paradigm shifts in experience.
IV. Agentic Organizations — DAOs Without CEOs
The end of corporations. The birth of autonomous orgs.
In 2022, Sam Altman redefined “tools.”
In 2025, we’ll redefine “organizations.”
Future orgs won’t be hierarchies. They’ll be networks of autonomous agents.
Agents are the new work unit. They don’t sleep. They learn continuously. They self-schedule.
They’re not tools to help humans — they are the operating system of post-human orgs.
What’s coming:
- DAOs with agent-driven governance and privacy.
- Smart Widgets that deploy trade/social/payment agents in three lines of code.
- Privacy as a default layer in automation.
- A new generation of AI-native hackathon projects.
AI + blockchain isn’t a buzzword. It’s the genesis of organizational intelligence.
Yesterday, the company was an information processor.
Tomorrow, the DAO is an autonomous agent network.
No CEOs. No approvals. No offices. Just coordination at the speed of compute.
The Bet: BUIDL Freedom for Humanity
FDA Free Society. Open Source Quantum. Consumer Crypto. Agentic Orgs.
These are not sci-fi. They are already happening.
At Dora Ventures, we don’t just back technologies.
We back builders who say:
“The system is broken — and I’m going to fix it myself.”
We back rebels who reject stagnation.
Who write code instead of complaints.
Who build networks instead of narratives.
Who refuse to ask permission to build the future.
Hackers are eating the world.
And in the age of AI, humanity will only survive if it chooses to become hackers — to use code, coordination, and imagination to build a world worth living in.
Let’s build.
-
 @ 04ff5a72:22ba7b2d
2025-03-19 03:25:28
@ 04ff5a72:22ba7b2d
2025-03-19 03:25:28The Evolution of the "World Wide Web"
The internet has undergone a remarkable transformation since its inception, evolving from a collection of static pages to a dynamic, interconnected ecosystem, and now progressing toward a decentralized future. This evolution is commonly divided into three distinct phases: Web 1, Web 2, and the emerging Web 3. Each phase represents not only technological advancement but fundamental shifts in how we interact with digital content, who controls our data, and how value is created and distributed online. While Web 1 and Web 2 have largely defined our internet experience to date, Web 3 promises a paradigm shift toward greater user sovereignty, decentralized infrastructure, and reimagined ownership models for digital assets.
The Static Beginning: Web 1.0
The first iteration of the web, commonly known as Web 1.0, emerged in the early 1990s and continued until the late 1990s. This period represented the internet's infancy, characterized by static pages with limited functionality and minimal user interaction[1]. At the core of Web 1 was the concept of information retrieval rather than dynamic interaction.
Fundamental Characteristics of Web 1
During the Web 1 era, websites primarily served as digital brochures or informational repositories. Most sites were static, comprised of HTML pages containing fixed content such as text, images, and hyperlinks[1]. The HTML (Hypertext Markup Language) provided the structural foundation, while CSS (Cascading Style Sheets) offered basic styling capabilities. These technologies enabled the creation of visually formatted content but lacked the dynamic elements we take for granted today.
The Web 1 experience was predominantly one-directional. The majority of internet users were passive consumers of content, while creators were primarily web developers who produced websites with mainly textual or visual information[2]. Interaction was limited to basic navigation through hyperlinks, with few opportunities for users to contribute their own content or engage meaningfully with websites.
Technical limitations further defined the Web 1 experience. Information access was significantly slower than today's standards, largely due to the prevalence of dial-up connections. This constraint meant websites needed to be optimized for minimal bandwidth usage[1]. Additionally, security measures were rudimentary, making early websites vulnerable to various cyberattacks without adequate protection systems in place.
The Social Revolution: Web 2.0
As the internet matured in the late 1990s and early 2000s, a significant transformation occurred. Web 2.0 emerged as a more dynamic, interactive platform that emphasized user participation, content creation, and social connectivity[6]. This shift fundamentally changed how people engaged with the internet, moving from passive consumption to active contribution.
The Rise of Social Media and Big Data
Web 2.0 gave birth to social media platforms, interactive web applications, and user-generated content ecosystems. Companies like Google, Facebook, Twitter, and Amazon developed business models that leveraged user activity and content creation[4]. These platforms transformed from simple information repositories into complex social networks and digital marketplaces.
Central to the Web 2.0 revolution was the collection and analysis of user data on an unprecedented scale. Companies developed sophisticated infrastructure to handle massive amounts of information. Google implemented systems like the Google File System (GFS) and Spanner to store and distribute data across thousands of machines worldwide[4]. Facebook developed cascade prediction systems to manage user interactions, while Twitter created specialized infrastructure to process millions of tweets per minute[4].
These technological advancements enabled the monetization of user attention and personal information. By analyzing user behavior, preferences, and social connections, Web 2.0 companies could deliver highly targeted advertising and personalized content recommendations. This business model generated immense wealth for platform owners while raising significant concerns about privacy, data ownership, and the concentration of power in the hands of a few technology giants.
The Decentralized Future: Web 3.0
Web 3 represents the next evolutionary stage of the internet, characterized by principles of decentralization, transparency, and user sovereignty[6]. Unlike previous iterations, Web 3 seeks to redistribute control from centralized entities to individual users and communities through blockchain technology and decentralized protocols.
Blockchain as the Foundation
The conceptual underpinnings of Web 3 emerged with the creation of Bitcoin in 2009. Bitcoin introduced a revolutionary approach to digital transactions by enabling peer-to-peer value transfer without requiring a central authority. This innovation demonstrated that trust could be established through cryptographic proof rather than relying on traditional financial institutions.
Ethereum expanded upon Bitcoin's foundation by introducing programmable smart contracts, which allowed for the creation of decentralized applications (dApps) beyond simple financial transactions. This breakthrough enabled developers to build complex applications with self-executing agreements that operate transparently on the blockchain[6].
Ownership and Data Sovereignty
A defining characteristic of Web 3 is the emphasis on true digital ownership. Through blockchain technology and cryptographic tokens, individuals can now assert verifiable ownership over digital assets in ways previously impossible[6]. This stands in stark contrast to Web 2 platforms, where users effectively surrendered control of their content and data to centralized companies.
The concept of self-custody exemplifies this shift toward user sovereignty. Platforms like Trust Wallet enable individuals to maintain control over their digital assets across multiple blockchains without relying on intermediaries[5]. Users hold their private keys, ensuring that they—not corporations or governments—have ultimate authority over their digital property.
Decentralized Physical Infrastructure Networks (DePIN)
Web 3 extends beyond digital assets to reimagine physical infrastructure through Decentralized Physical Infrastructure Networks (DePIN). These networks connect blockchain technology with real-world systems, allowing people to use cryptocurrency tokens to build and manage physical infrastructure—from wireless hotspots to energy systems[7].
DePIN projects decentralize ownership and governance of critical infrastructure, creating more transparent, efficient, and resilient systems aligned with Web 3 principles[7]. By distributing control among network participants rather than centralizing it within corporations or governments, these projects bridge the gap between digital networks and physical reality.
Non-Fungible Tokens and Intellectual Property
Non-Fungible Tokens (NFTs) represent another revolutionary aspect of Web 3, providing a mechanism for verifying the authenticity and ownership of unique digital items. NFTs enable creators to establish provenance for digital art, music, virtual real estate, and other forms of intellectual property, addressing longstanding issues of duplication and unauthorized distribution in the digital realm[6].
This innovation has profound implications for creative industries, potentially enabling more direct relationships between creators and their audiences while reducing dependence on centralized platforms and intermediaries.
Nostr: A Decentralized Protocol for Social Media and Communication
Nostr (Notes and Other Stuff Transmitted by Relays) is a decentralized and censorship-resistant communication protocol designed to enable open and secure social networking. Unlike traditional social media platforms that rely on centralized servers and corporate control, Nostr allows users to communicate directly through a network of relays, ensuring resilience against censorship and deplatforming.
The protocol operates using simple cryptographic principles: users generate a public-private key pair, where the public key acts as their unique identifier, and messages are signed with their private key. These signed messages are then broadcast to multiple relays, which store and propagate them to other users. This structure eliminates the need for a central authority to control user identities or content distribution[8].
As concerns over censorship, content moderation, and data privacy continue to rise, Nostr presents a compelling alternative to centralized social media platforms. By decentralizing content distribution and giving users control over their own data, it aligns with the broader ethos of Web3—empowering individuals and reducing reliance on corporate intermediaries[9].
Additionally Nostr implements a novel way for users to monetize their content via close integration with Bitcoin's "Lightning Network"[11] -- a means by which users are able to instantly transmit small sums (satoshi's, the smallest unit of Bitcoin) with minimal fees. This feature, known as “zapping,” allows users to send micropayments directly to content creators, tipping them for valuable posts, comments, or contributions. By leveraging Lightning wallets, users can seamlessly exchange value without relying on traditional payment processors or centralized monetization models. This integration not only incentivizes quality content but also aligns with Nostr’s decentralized ethos by enabling peer-to-peer financial interactions that are censorship-resistant and borderless.
For those interested in exploring Nostr, setting up an account requires only a private key, and users can begin interacting with the network immediately by selecting a client that suits their needs. The simplicity and openness of the protocol make it a promising foundation for the next generation of decentralized social and communication networks.
Alternative Decentralized Models: Federation
Not all Web 3 initiatives rely on blockchain technology. Platforms like Bluesky are pioneering federation approaches that allow users to host their own data while maintaining seamless connectivity across the network[10]. This model draws inspiration from how the internet itself functions: just as anyone can host a website and change hosting providers without disrupting visitor access, Bluesky enables users to control where their social media data resides.
Federation lets services be interconnected while preserving user choice and flexibility. Users can move between various applications and experiences as fluidly as they navigate the open web[10]. This approach maintains the principles of data sovereignty and user control that define Web 3 while offering alternatives to blockchain-based implementations.
Conclusion
The evolution from Web 1 to Web 3 represents a profound transformation in how we interact with the internet. From the static, read-only pages of Web 1 through the social, data-driven platforms of Web 2, we are now entering an era defined by decentralization, user sovereignty, and reimagined ownership models.
Web 3 technologies—whether blockchain-based or implementing federation principles—share a common vision of redistributing power from centralized entities to individual users and communities. By enabling true digital ownership, community governance, and decentralized infrastructure, Web 3 has the potential to address many of the concerns that have emerged during the Web 2 era regarding privacy, control, and the concentration of power.
As this technology continues to mature, we may witness a fundamental reshaping of our digital landscape toward greater transparency, user autonomy, and equitable value distribution—creating an internet that more closely aligns with its original promise of openness and accessibility for all.
Sources
[1] What is WEB1? a brief history of creation - White and Partners https://whiteand.partners/en/what-is-web1-a-brief-history-of-creation/ [2] Evolution of the Internet - from web1.0 to web3 - LinkedIn https://www.linkedin.com/pulse/evolution-internet-from-web10-web3-ravi-chamria [3] Web3 Social: Create & Monetize with Smart Contracts - Phala Network https://phala.network/web3-social-create-monetize-with-smart-contracts [4] [PDF] Big Data Techniques of Google, Amazon, Facebook and Twitter https://www.jocm.us/uploadfile/2018/0613/20180613044107972.pdf [5] True crypto ownership. Powerful Web3 experiences - Trust Wallet https://trustwallet.com [6] Web3: Revolutionizing Digital Ownership and NFTs - ThoughtLab https://www.thoughtlab.com/blog/web3-revolutionizing-digital-ownership-and-nfts/ [7] DePIN Crypto: How It's Revolutionizing Infrastructure in Web3 https://www.ulam.io/blog/how-depin-is-revolutionizing-infrastructure-in-the-web3-era [8] Nostr: Notes and Other Stuff… https://nostr.com/ [9] Nostr: The Importance of Censorship-Resistant Communication... https://bitcoinmagazine.com/culture/nostr-the-importance-of-censorship-resistant-communication-for-innovation-and-human-progress- [10] Bluesky: An Open Social Web https://bsky.social/about/blog/02-22-2024-open-social-web [11] Wikipedia: Lightning Network https://en.wikipedia.org/wiki/Lightning_Network
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ a60e79e0:1e0e6813
2025-03-18 15:38:25
@ a60e79e0:1e0e6813
2025-03-18 15:38:25**This is a long form note test of a post that lives on my Nostr educational website Hello Nostr **
One of the first things most people learn when getting started with Nostr is the importance of their private key, or ‘nsec’. The nsec is the key to their Nostr world. Whoever controls an nsec, controls that account. Lose access to the nsec and you lose access to that account and its social graph.
So the nsec is very important and should be treated very carefully, but what happens if we want to use or test multiple Nostr clients? Newer clients might be malicious, or have unknown security vulnerabilities, so simply go pasting our nsec everywhere just to see if we like a new app is not the best idea!
Thankfully there are solutions for nsec management that allow us to do exactly that, without having to expose our all important nsec to each and every app we want to interact with. The most commonly used to date are browser extensions like Alby or nos2x. Typically these types of browser extensions do not work on mobile platforms.
Enter Amber…
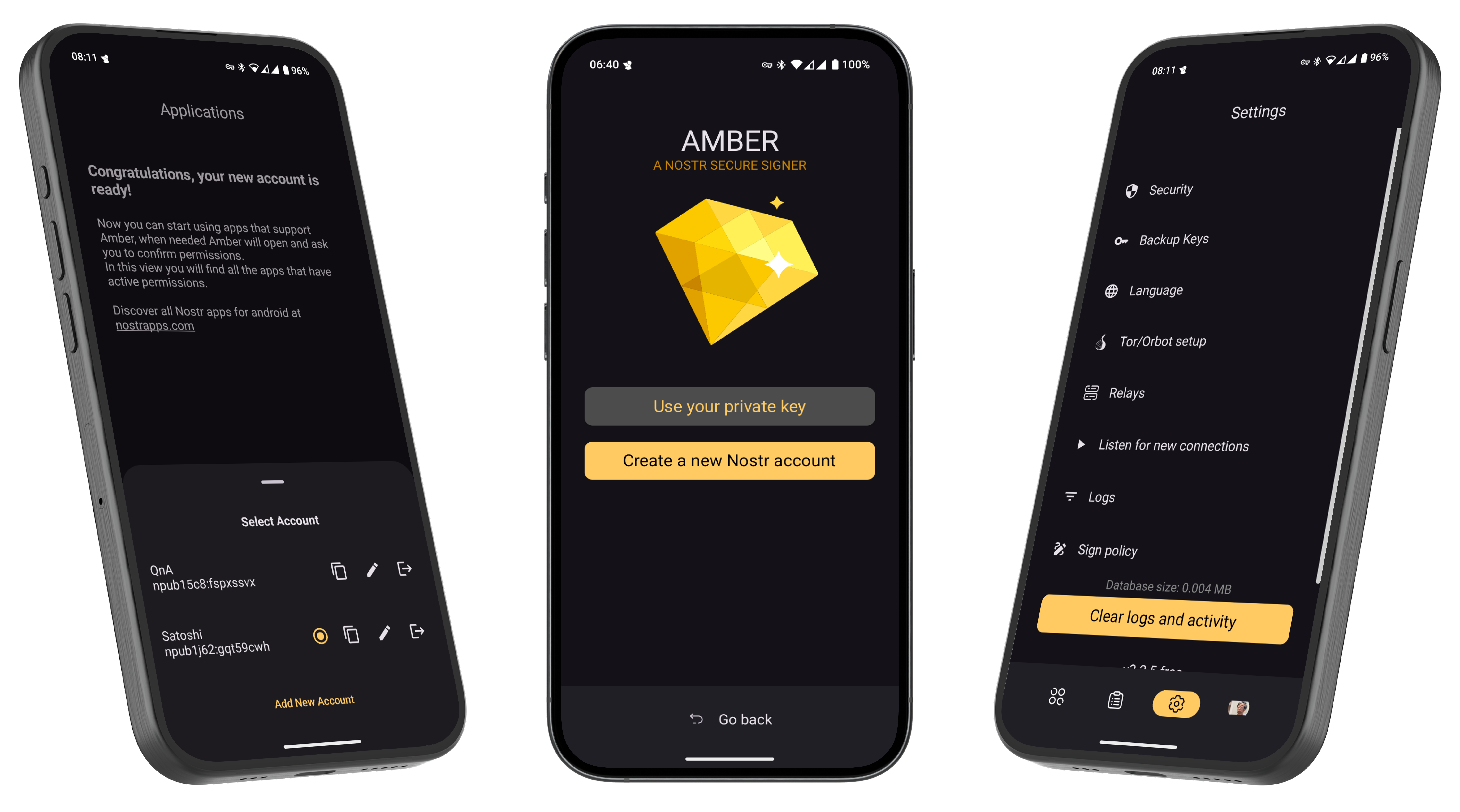
What is Amber?
Amber is a free and open source Android application that serves as a dedicated ‘Nostr event signer’. Amber allows users to keep their nsec segregated in a single, dedicated app. The goal of Amber is to have your smartphone act as a NIP-46 signing device without any need for servers or additional hardware.
At its core Amber serves two main purposes:
Securing your nsec(s) Using this nsec to sign events for other Nostr clients on your phone
Got an iPhone? Check out nsec.app
Getting Started
- Download Amber to your phone. It is available from Zap Store, Obtanium, GitHub or F-Droid
Download Amber here. Support Amber here.
-
When opening Amber for the first time, you’ll have the option to create a new Nostr account (nsec) or import an existing one.
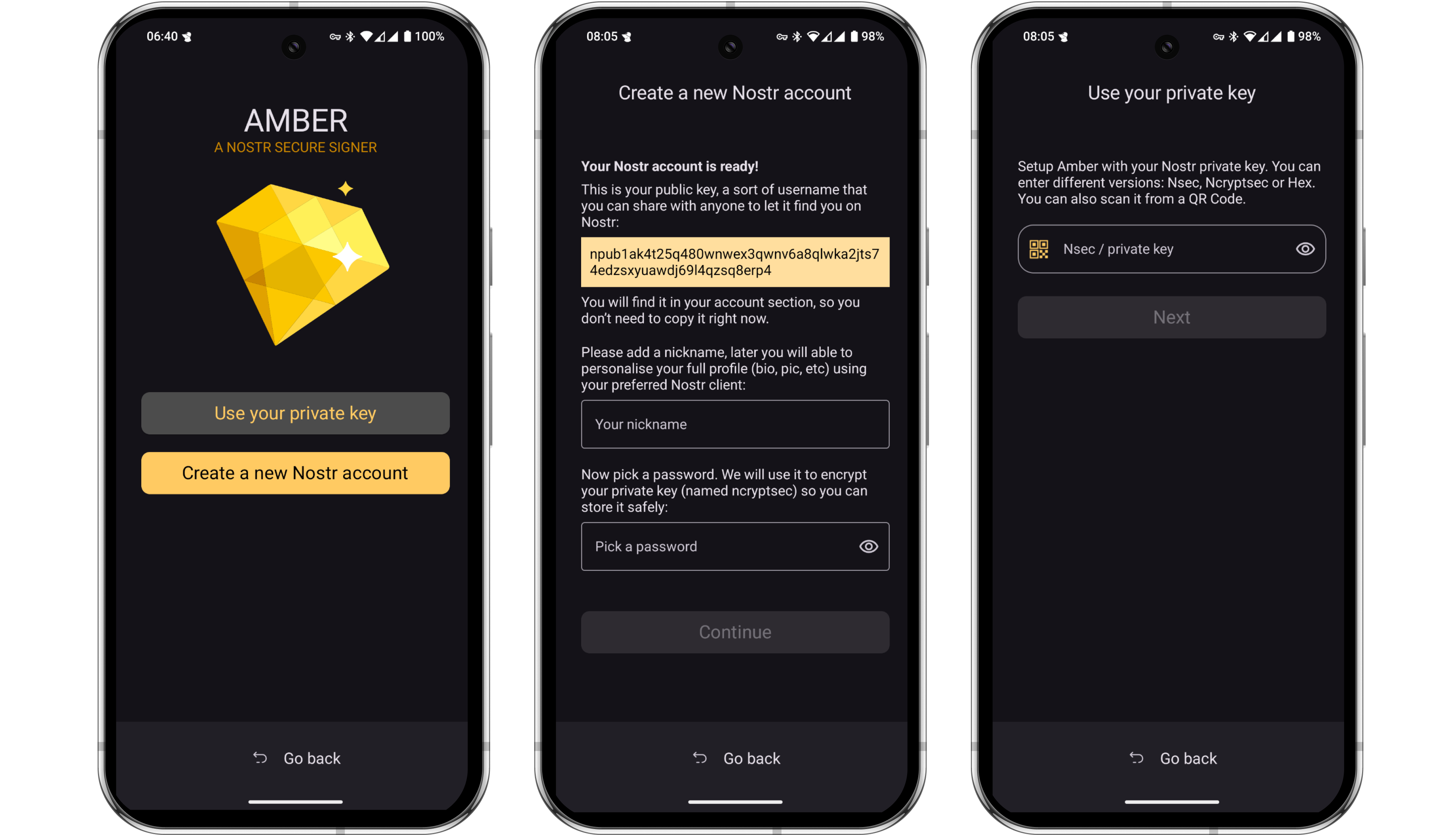
-
If you do not currently have a Nostr account, Amber will help you generate and secure a brand new nsec. Amber allows you to download an encrypted file containing your nsec as well as the option to download a human-readable version of the nsec in the form of 12 English words, similar to a Bitcoin seed.
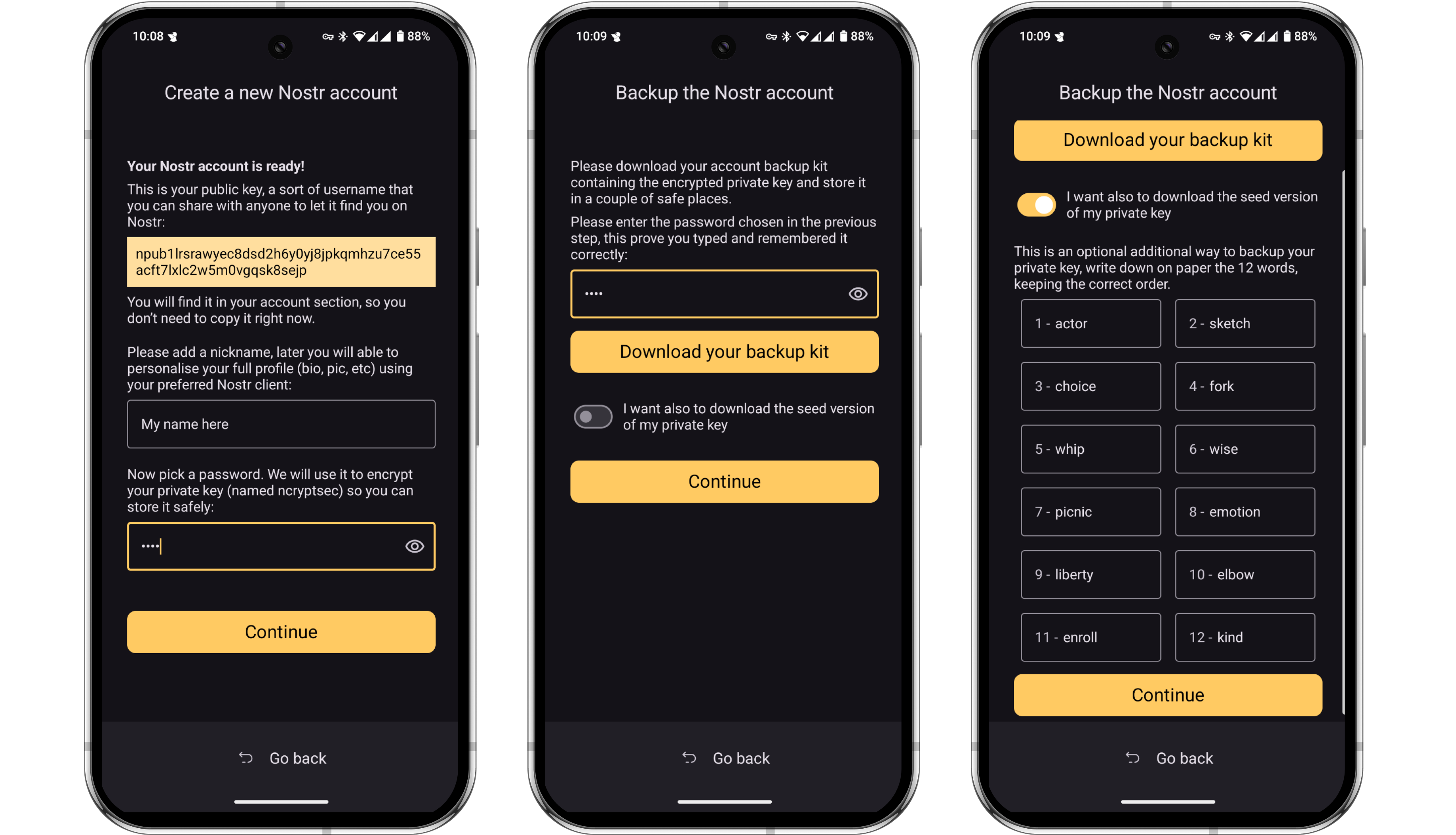
Skip this step if you have an existing nsec that you want to import to Amber.
-
To import an existing nsec, choose ‘Use your private key’. You can then paste the nsec from an existing client, or scan a QR code of it if you have one available to you.
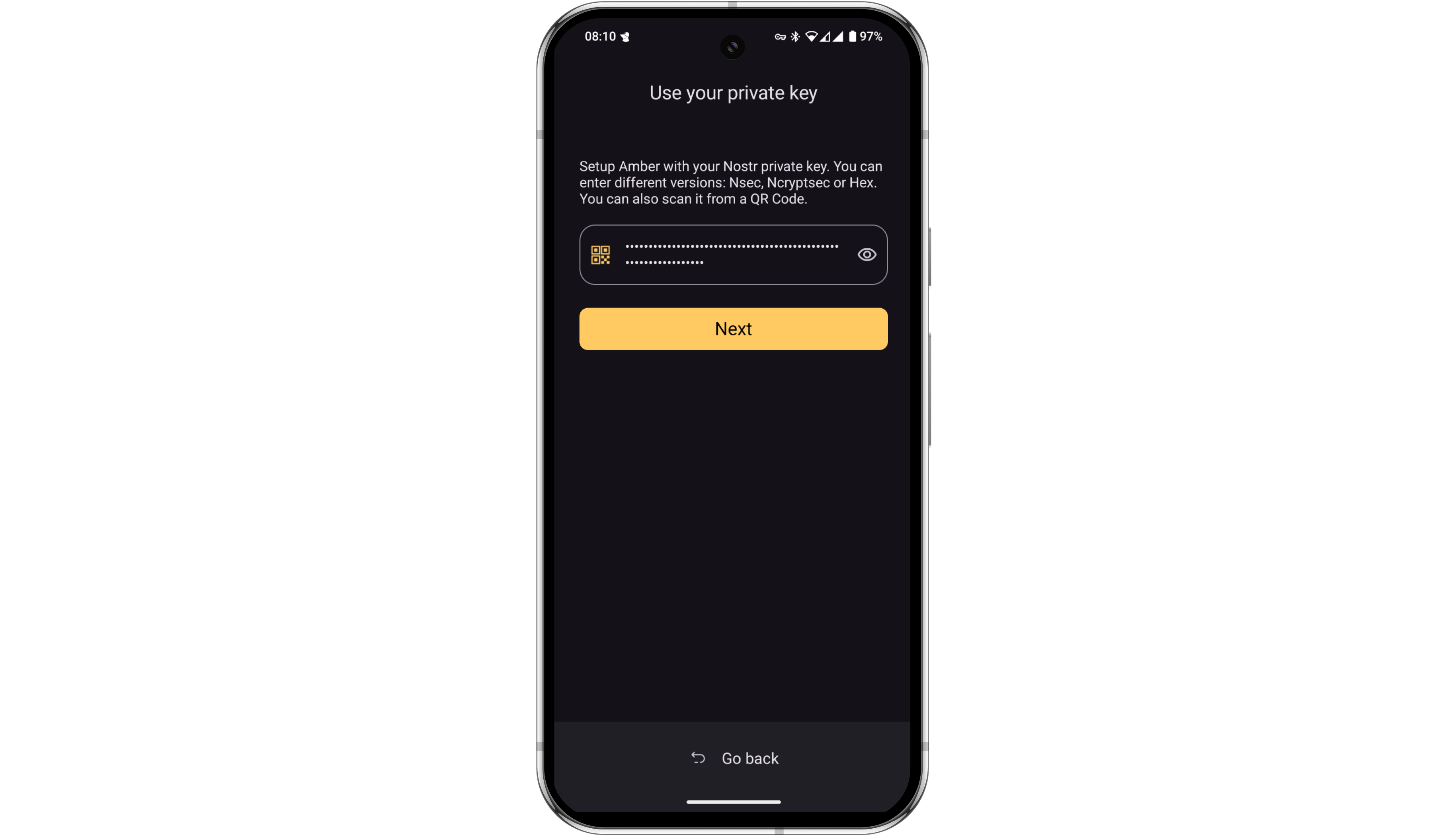
-
Once you have created or imported your nsec, Amber will ask for some basic permissions. You can allow the app the approve basic actions, or enable more granular selection for each client you subsequently connect. Once you tap ‘Finish’, you’ll see that the account is now ready.
If you have or require more than one Nostr account, you can repeat these steps for each one. All accounts can be viewed by tapping the profile image in the bottom right corner of the screen.
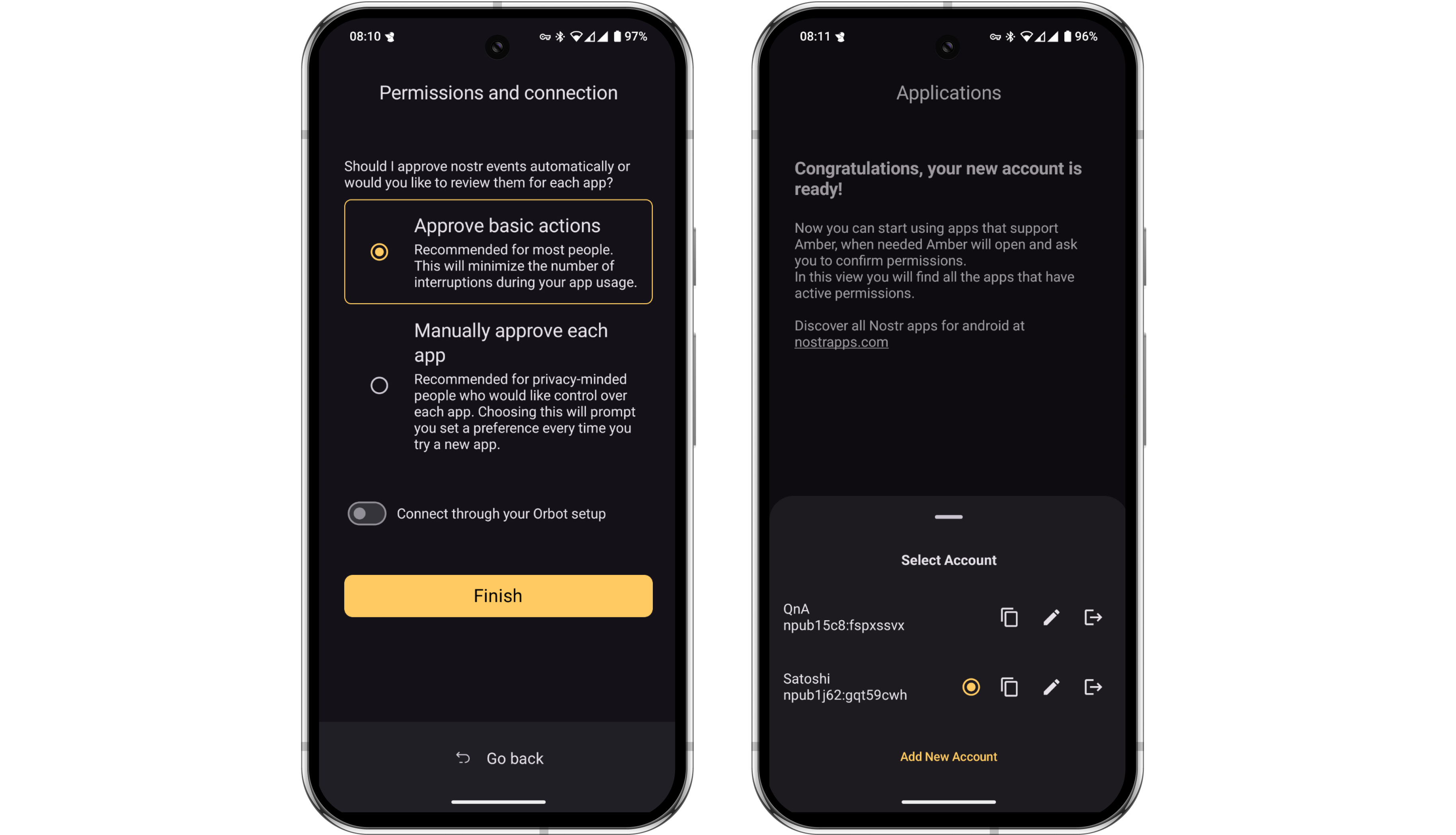
- That’s it, Amber is now ready to sign events. Amber allows multiple ways to connect other clients to it, but most will have a very simple ‘Login with Amber’ button. Let’s demo this in practice with Amethyst, the most popular Android-only client.
The opening screen of Amethyst shows the ‘Login with Amber’ option. Tap that.
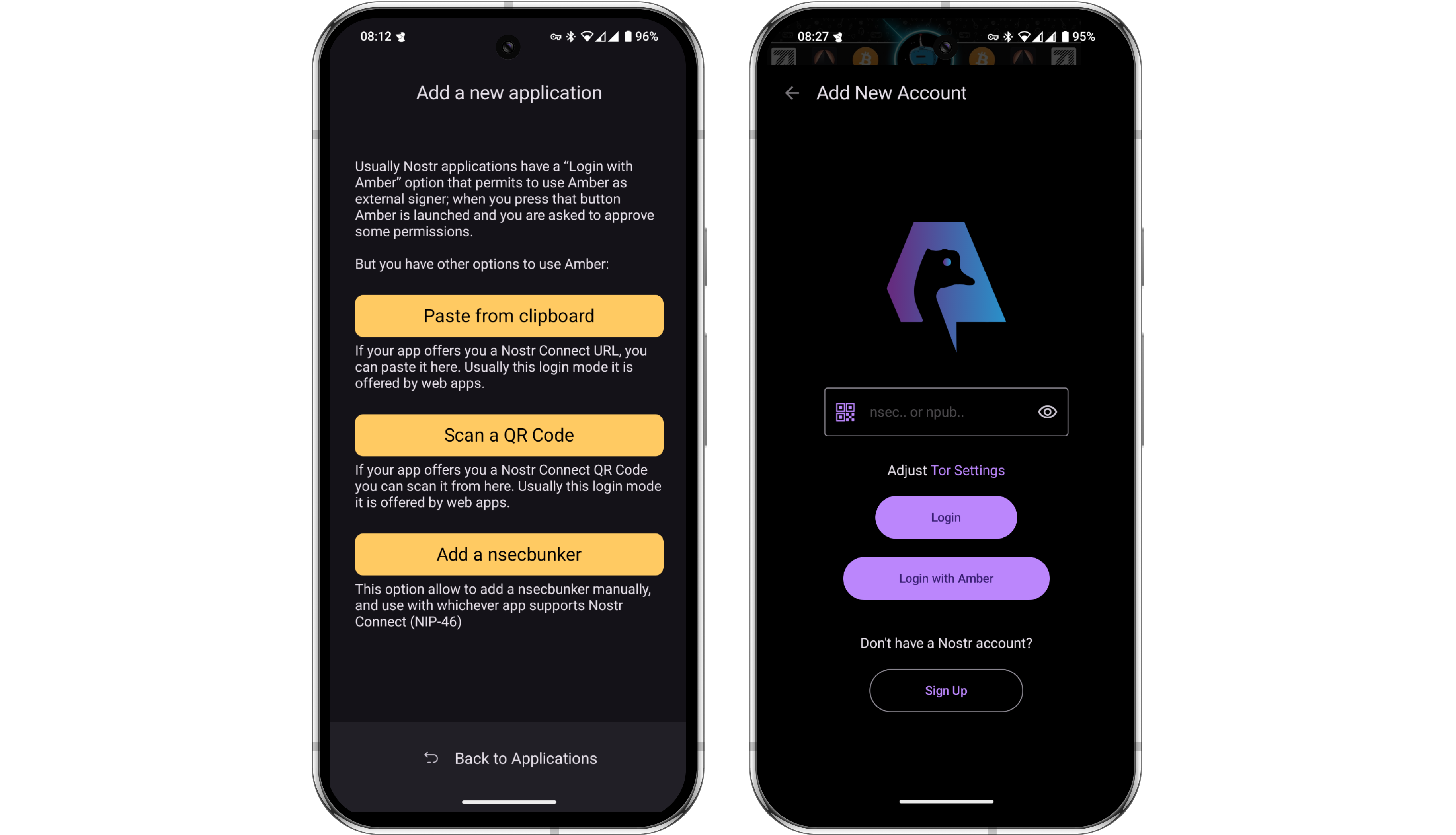
- Amber will then open automatically and ask you to define the level of autonomy you’d like to have with Amethyst. This setting defines how often Amber will require you to manually authorize each event.
For example, you might want Amber to automatically sign every like or repost you do in Amethyst, but then be asked to manually approve all direct messages sent from your account. These permissions can be customized in the settings at any time.
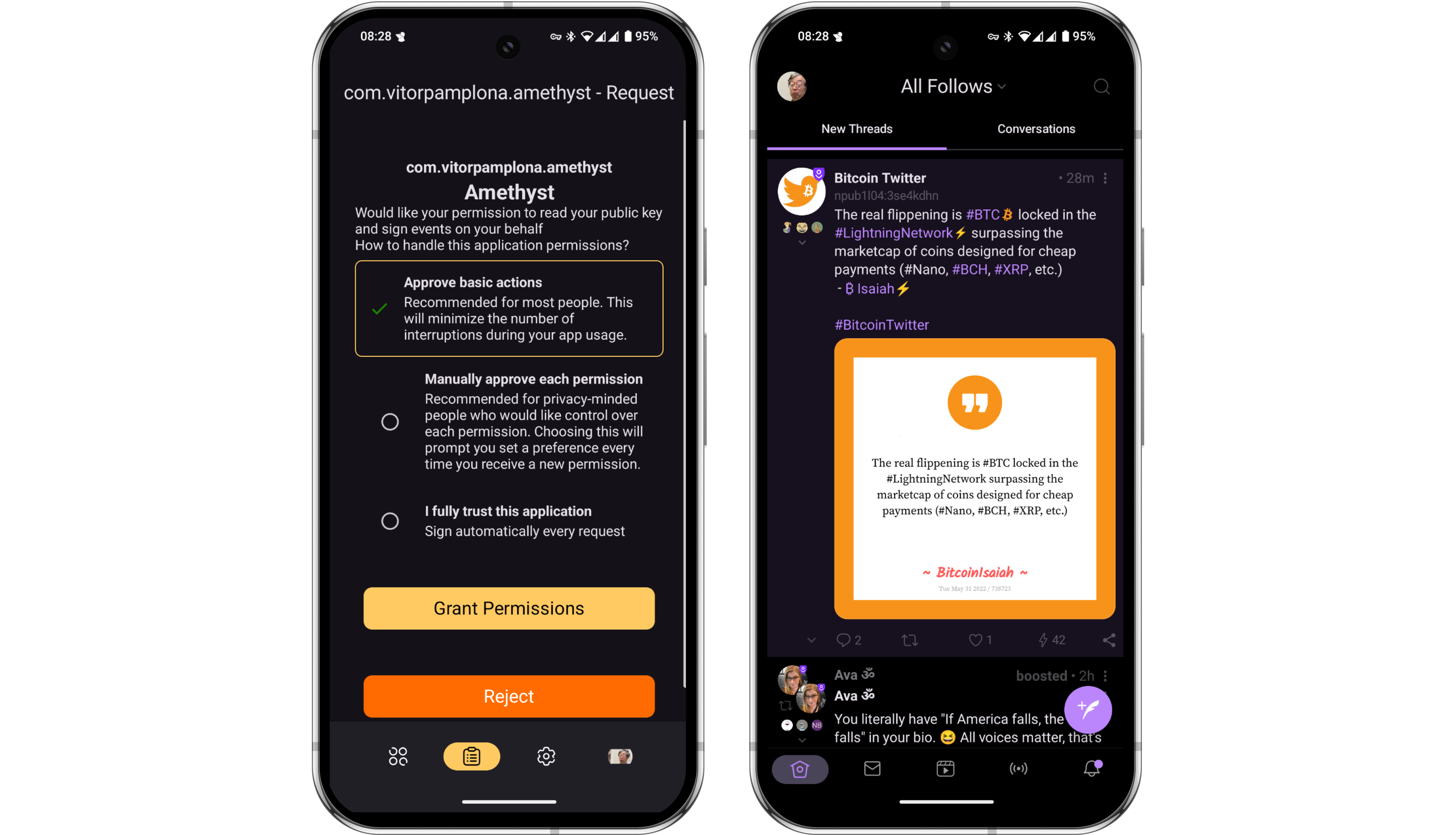
- Let’s assume that upon setup, we did not grant Amber the ability to automatically sign short text notes for us. Let’s look at how simple the authorization flow is. Type a new short note in Amethyst and press ‘Post’.
Amethyst will instantly send the request to the Amber app on your phone, with no third party server involved. Amber will open and ask you to approve the event. When you do, Amber signs the event with the nsec it stores for you and automatically send the signed event back to Amethyst to be posted. The whole process takes just a few seconds.
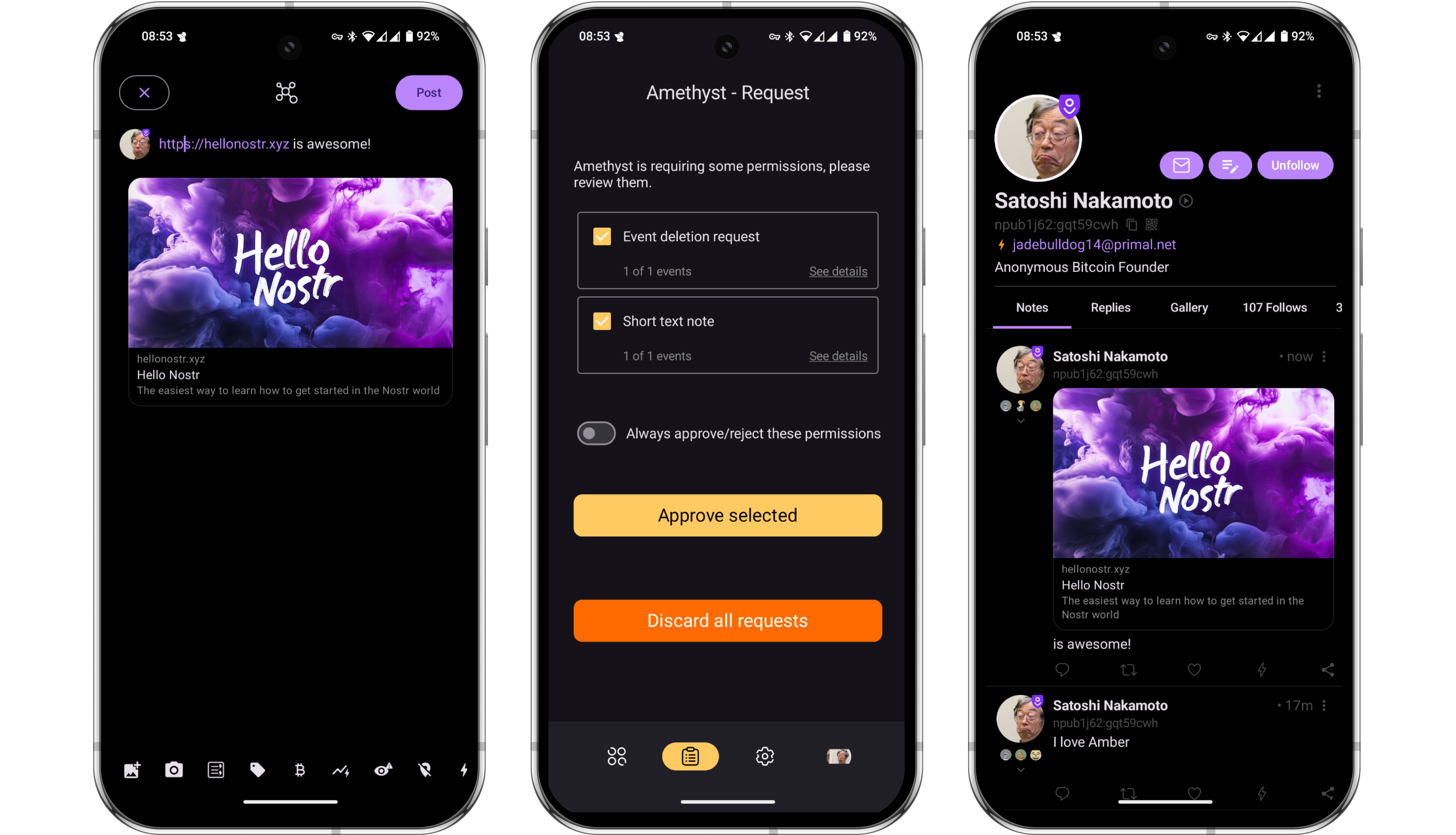
Using Amber with a Web Client
-
Next let’s take a look at how you can use Amber on your phone to sign events on a web app running on your computer. For this example, we’ll be using Coracle. Open Coracle and click ‘Log In’, then choose ‘Use Remote Signer’. Coracle will then display a QR code.
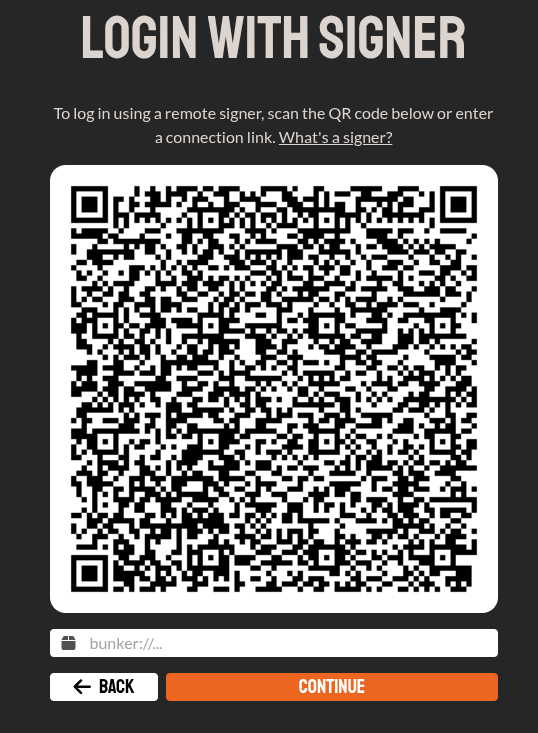
-
Open Amber and navigate to the Applications page, tap the + icon, then scan the QR code being displayed by Coracle.
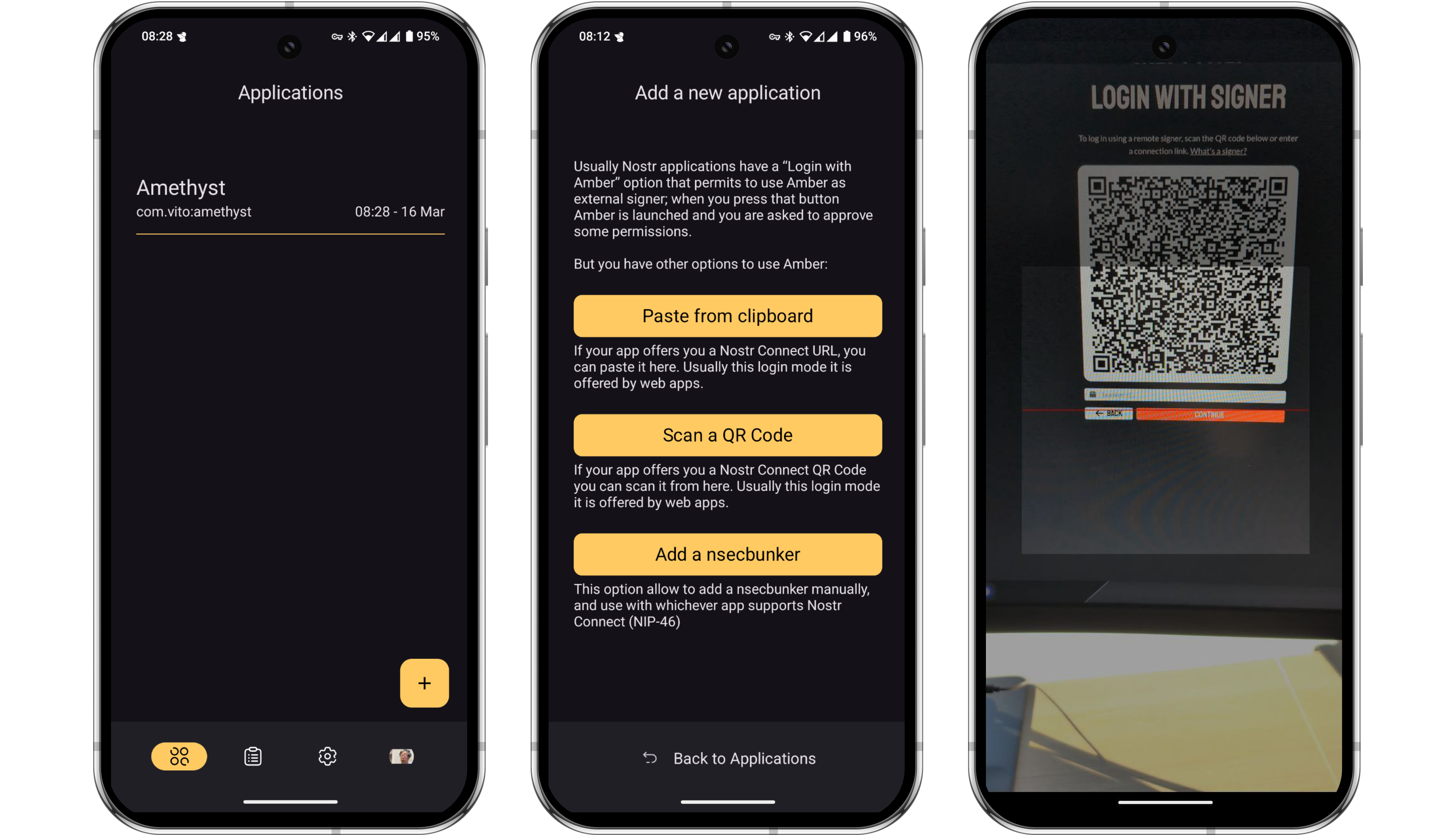
-
Just as it did earlier with Amethyst, Amber will now ask you to grant some basic permissions for the Coracle connection. Once again, these permissions can be customized at any time in the settings. Once granted, you’ll notice that Coracle automatically logs in to your feed.
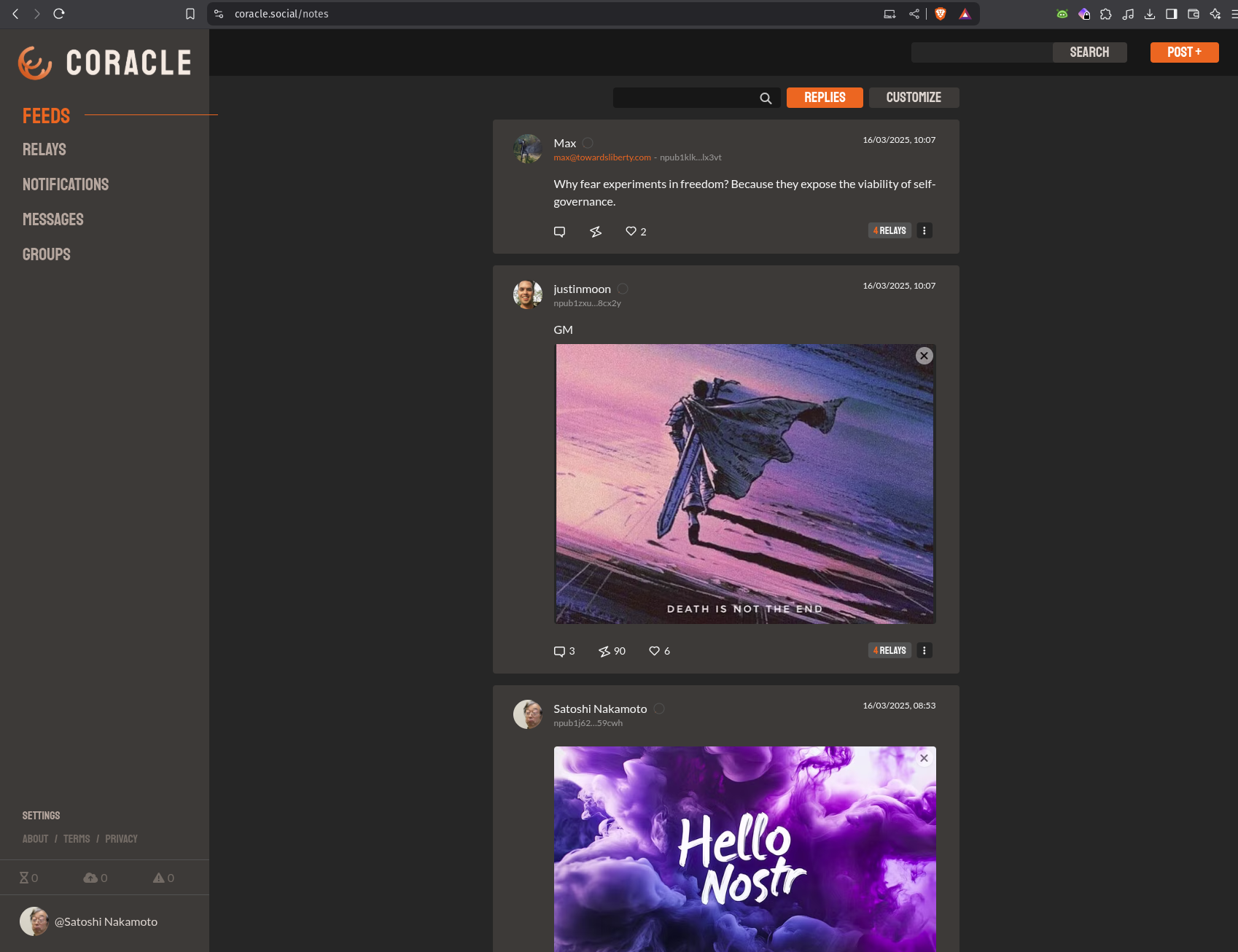
But wait, how did that happen? The nsec is in Amber on your phone, and Coracle is running on your computer. The two might not even be in the same location or on the same network!? The communication is happening over the Nostr protocol, via relays. Which relays are used for this communication can be configured in the Amber settings.
-
Let’s test out a short note on Coracle to demonstrate the signing process. Click ‘Post +’ in the top right corner, draft your note and then click send.
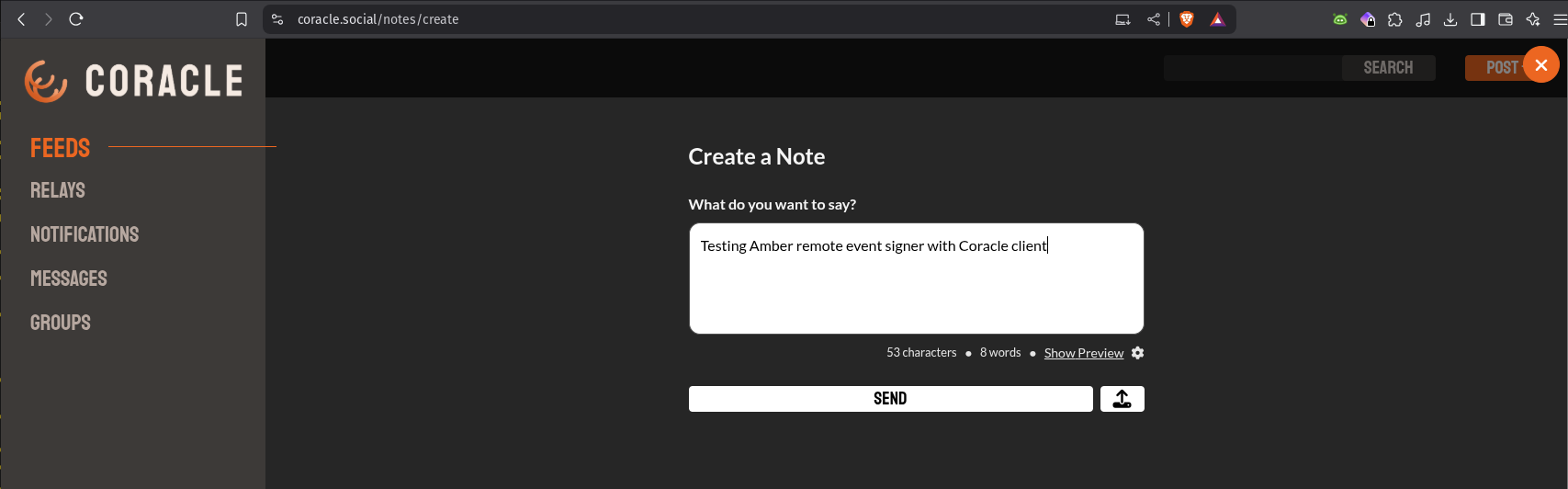
-
Amber will send a push notification to your phone. Tapping the notification will open Amber for you to approve the event.
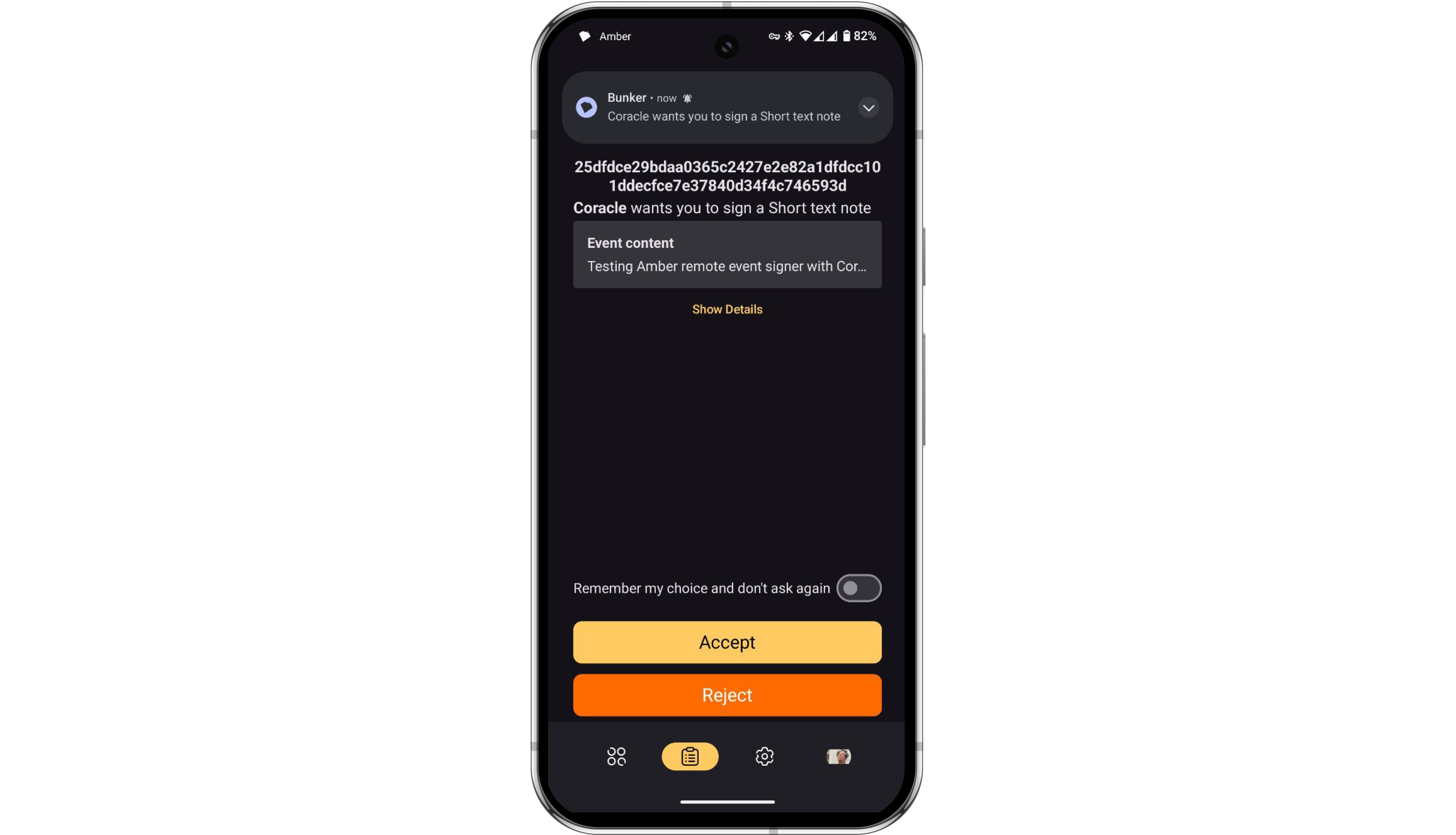
-
Once the event is approved in Amber, Amber will automatically send the signed event back to Coracle for publishing.
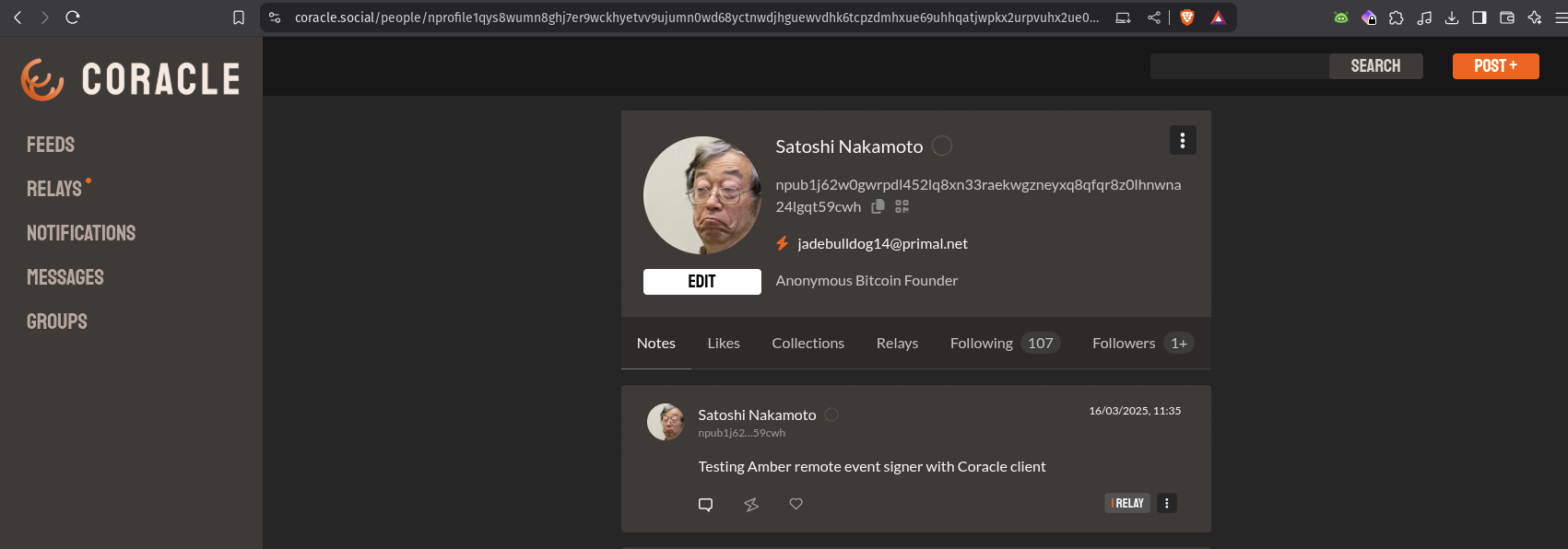
Summary
You can view Amber as a vault for your Nostr private keys (nsec). It allows you to explore the entire ecosystem without exposing your nsec to every new app you try. Amber is an incredibly simple yet powerful tool that belongs on the Android phone of every Nostr user.
At the time of writing, using Amber as a remote event signer is supported by the following popular Nostr clients:
- Amethyst (mobile)
- Coracle (web)
- 0xChat (mobile)
- Fountain (mobile)
- Zap Store (mobile)
- Keychat (mobile)
- Freeflow (mobile)
- Highlighter (web)
- Chachi Chat (web)
- Habla (web)
- Shopstr (web)
- Plebeian Market (web)
- Snort (web)
- Nostrudel (web)
If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I’ll be sure to Zap you back! ⚡️
-
 @ 21335073:a244b1ad
2025-03-18 14:23:35
@ 21335073:a244b1ad
2025-03-18 14:23:35Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ a012dc82:6458a70d
2025-03-27 14:23:51
@ a012dc82:6458a70d
2025-03-27 14:23:51The cryptocurrency market, known for its dramatic fluctuations, has always been a subject of intrigue and speculation. Bitcoin, as the pioneering digital currency, has been at the epicenter of this financial whirlwind. As we approach 2024, the anticipation surrounding Bitcoin's value is palpable, with potential investors and seasoned cryptocurrency enthusiasts keenly eyeing the market's movements. This article aims to dissect the recent forecasts for Bitcoin's price in the coming year, delve into the multifaceted factors influencing these predictions, and explore the broader implications for those contemplating an investment in Bitcoin.
Table of Contents
-
2024 Bitcoin Price Predictions: A New Peak on the …
-
Key Factors Driving Bitcoin's Price
-
The Halving Event
-
Institutional Interest and ETFs
-
Economic and Monetary Policies
-
-
The Debate: To Buy or Not to Buy
-
Risk Tolerance
-
Market Dynamics
-
Long-Term Perspective
-
-
Caution and Speculation
-
Conclusion
-
FAQs
2024 Bitcoin Price Predictions: A New Peak on the Horizon
Recent analyses, particularly a notable report from UK fintech firm Finder, have painted an optimistic picture for Bitcoin in 2024. Experts within the field are forecasting a new zenith for Bitcoin, projecting it to reach an all-time high of $88,000, with expectations of the currency stabilizing around $77,000 by the end of the year. These projections represent a significant uptick from Bitcoin's current valuation and suggest a potentially lucrative year ahead for the digital currency. However, it's crucial to recognize that these predictions are not guarantees but educated guesses based on current market trends and historical data. The cryptocurrency market's inherent volatility means that while the potential for substantial gains exists, so too does the risk of dramatic losses. Investors should approach these predictions with cautious optimism, considering the broader economic and technological landscape that could impact Bitcoin's trajectory.
Key Factors Driving Bitcoin's Price
The anticipated surge in Bitcoin's value can be attributed to several key factors, each playing a pivotal role in shaping the currency's future:
The Halving Event
The Bitcoin halving event scheduled for April 2024 stands as a significant milestone. This event, which occurs approximately every four years, reduces the reward for mining Bitcoin transactions by half. Historically, halving events have led to a decrease in the supply of new Bitcoins entering the market, which, in turn, has led to price increases as demand outstrips supply. The 2024 halving is expected to follow this trend, contributing to the bullish outlook for Bitcoin's price. However, while past performance can offer insights, it is not indicative of future results. The halving's impact could be influenced by a myriad of factors, including changes in miner behavior, technological advancements, and shifts in investor sentiment.
Institutional Interest and ETFs
Another driving force behind the optimistic price predictions is the growing institutional interest in Bitcoin and the approval of Bitcoin ETFs in the United States. These developments have not only legitimized Bitcoin as an investment asset but also made it more accessible to a broader audience of traditional investors. The introduction of ETFs has bridged the gap between the conventional financial world and the burgeoning cryptocurrency market, providing a regulated and familiar avenue for investment. However, the influx of institutional money also brings new challenges, including increased market manipulation risks and the potential for regulatory crackdowns. Investors should remain vigilant, monitoring the evolving landscape and considering the long-term implications of institutional involvement in the cryptocurrency space.
Economic and Monetary Policies
Global economic conditions and monetary policies, particularly those enacted by the US Federal Reserve, are also critical factors influencing Bitcoin's price. In an environment of low interest rates and quantitative easing, investors have increasingly turned to alternative assets like Bitcoin as a hedge against inflation and currency devaluation. However, shifts in these policies could significantly impact investor behavior and market dynamics. A rise in interest rates or a tightening of monetary policy could lead to reduced liquidity in the market and a shift away from riskier assets, including Bitcoin. Conversely, continued economic uncertainty and inflationary pressures could bolster Bitcoin's appeal as a store of value.
The Debate: To Buy or Not to Buy
The decision to invest in Bitcoin, especially in light of the optimistic 2024 price predictions, is fraught with complexity:
Risk Tolerance
Bitcoin's notorious volatility cannot be overstated. The digital currency's price can experience dramatic swings within short periods, influenced by factors ranging from regulatory news to market sentiment. Potential investors must assess their risk tolerance and financial situation before entering the market. It's essential to consider whether you can withstand significant fluctuations in your investment's value and how such changes would impact your overall financial health.
Market Dynamics
Understanding the broader market dynamics and potential regulatory changes is crucial for anyone considering investing in Bitcoin. The cryptocurrency market does not operate in a vacuum; it is affected by global economic conditions, technological developments, and shifts in regulatory attitudes. Staying informed and adaptable is key, as today's market drivers could change rapidly, altering Bitcoin's price trajectory.
Long-Term Perspective
Adopting a long-term perspective is vital when investing in Bitcoin. While the allure of quick profits can be tempting, Bitcoin's history suggests that it is better suited as a long-term investment. The market's cyclical nature, characterized by boom-and-bust cycles, requires patience and a long-term outlook. Investors should avoid making impulsive decisions based on short-term price movements and instead focus on the underlying value and potential of Bitcoin as a revolutionary digital asset.
Caution and Speculation
Despite the bullish forecasts, a note of caution is warranted. The cryptocurrency market remains speculative, and while Bitcoin has established itself as the leading digital currency, its future is not guaranteed. The landscape is rife with uncertainties, from technological challenges to regulatory hurdles. Potential investors should approach Bitcoin with a balanced perspective, recognizing the possibilities while being acutely aware of the risks.
Conclusion
The predictions for Bitcoin's price in 2024 offer a glimpse into a potentially prosperous future for the digital currency. However, the decision to invest should not be taken lightly. Prospective investors must navigate a landscape marked by volatility, uncertainty, and rapid change. By thoroughly evaluating the market, staying informed about developments, and considering their long-term financial goals, individuals can make more informed decisions about their involvement in the Bitcoin market. Whether now is the right time to buy Bitcoin is a personal decision that depends on individual circumstances, risk tolerance, and investment strategy. As with any investment, there are no guarantees, but for those willing to embrace the risks, the rewards could be substantial.
FAQs
Why is Bitcoin expected to reach new highs in 2024? Bitcoin's price is expected to surge due to factors like the halving event, increasing institutional interest, the approval of Bitcoin ETFs, and global economic conditions that favor alternative investments.
What is a Bitcoin halving event? A Bitcoin halving event is when the reward for mining new blocks is halved, reducing the rate at which new bitcoins are generated. This event occurs approximately every four years and tends to impact the price due to reduced supply.
Are Bitcoin ETFs significant for individual investors? Yes, Bitcoin ETFs provide individual investors with a regulated and familiar way to gain exposure to Bitcoin without directly purchasing or storing the cryptocurrency, potentially increasing its accessibility and demand.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ ed84ce10:cccf4c2a
2025-03-18 14:19:19
@ ed84ce10:cccf4c2a
2025-03-18 14:19:19The Evolution of Hackathons: From Offline to Online, Powering Frontier Innovation Worldwide
Throughout the history of open-source platform technology, hackathons have been the launchpads for innovation—fueling breakthroughs, incubating the next generation of startups, and serving as the proving ground for builders. Over the past decade, DoraHacks has led the charge, driving the hacker movement and open-source revolution. We didn’t just witness the evolution of hackathons—we architected it.
The Online Revolution of Hackathons
Before 2020, hackathons were largely stuck in the physical world—you had to be in the room to participate. The idea of a fully online, global hackathon was a pipe dream. Then, DoraHacks.io changed everything. Suddenly, a developer in Africa could win funding from a hackathon hosted by a Silicon Valley company. Geographic barriers collapsed. Today, over 95% of hackathons happen online.
The Infrastructure Revolution: Making Hackathons 10x More Effective
DoraHacks relentlessly iterated on the hackathon model. We built BUIDL pages for real-time project showcases, a world-class hackathon organizer dashboard, MACI-powered decentralized privacy governance, and Grant DAOs that provide ongoing funding. The result? DoraHacks became the ultimate launchpad for hackers and early-stage builders.
The Ecosystem Revolution: Supercharging Open Innovation
DoraHacks became the backbone of Web3 innovation—from Ethereum, Solana, and BNB Chain to the next wave of blockchains like Aptos, Cosmos, Injective, TON, and Sonic. Since 2023, hackathons have expanded beyond crypto—quantum computing, commercial space tech, and AI-driven innovations are now being built on DoraHacks.
Rolling Hackathons and Uninterrupted BUIDLing - the New Standard for Ecosystem Growth
BUIDLs can be created spontaneously at any time. Hosting Hackathons as short-term events held only once or twice a year is not conducive to attracting outstanding Hackers and high-quality projects to join the ecosystem and drive innovation in the long term. To remediate this, Hackathons should be continuous and uninterrupted, serving as a long-term driving force within the developer ecosystem.
Historically, the high organizational costs and substantial resource investments associated with frequent Hackathons meant that most emerging ecosystems couldn't afford to host them regularly. As a result, Hackathons became rare, annual spectacles, and for some projects, an unaffordable luxury. This model severely restricted developers' chances to participate and hindered the ecosystem's ability to innovate consistently. Let's imagine what would happen if an ecosystem held 12 or more Hackathons each year?
- Developers have a clear loyalty incentive: They would know that the ecosystem is committed to supporting and funding excellent developers and projects continuously, which would encourage them to make long-term investments and contribute regularly.
- Missing out is no longer an issue: Even if a developer couldn't attend a particular Hackathon, there would be another one soon, increasing accessibility.
- Accelerated ecosystem innovation: Frequent Hackathons would accelerate ecosystem innovation. Developers would be constantly pushed to explore new directions, significantly boosting the growth rate of the technological ecosystem.
Previously, due to the limitations of costs and organizational difficulties, frequent Hackathons were almost unthinkable. Only ecosystems with sufficient funds like Google and Amazon could afford rolling Hackathons. But now, DoraHacks' upcoming BUIDL AI platform tools are set to change the game. These tools make it possible to organize 12 Hackathons in a year, and even go a step further by enabling the simultaneous hosting of multiple differently-themed Hackathons. This will help emerging ecosystems effectively incentivise developers, expand their technological influence, and increase the number of exceptional BUIDLs (projects) in their ecosystems.
The majority of BUIDLs come about continuously and spontaneously and should be recognized and incentivized promptly, rather than having to wait for the single annual Hackathon.
As the saying goes, "He who wins over developers wins the world." In the highly competitive Web3 space, Hackathons are an effective means of attracting developers, and rolling Hackathons are the best way to achieve this. For an ecosystem to stay competitive, it must ensure that developers always have opportunities to engage and create.
The AI Era of Hackathons: A 10x Opportunity, A 10x Challenge
AI Turns Everyone Into a Hacker
AI has obliterated repetitive work. Building is faster than ever. Anyone, from anywhere, can hack, ship, and scale with AI tools that accelerate ideation, development, and execution. The potential of hackathons in this AI-powered era is 10x bigger than ever before.
But Hackathon Infrastructure Is Stuck in the Past
Despite this massive opportunity, organizing hackathons remains painfully inefficient:
- Most organizations don’t know how to run hackathons effectively.
- Even those who do lack time and resources to do it frequently.
- Ecosystem builders who have the resources can only host one hackathon per year.
The result?
- Hackathons are underutilized, slowing innovation.
- Ecosystem growth is bottlenecked by developer relations (DevRel) teams.
- Many ecosystems fail to maximize the potential of hackathons.
- Low-frequency hackathons waste hacker potential—builders sit idle when they could be shipping.
BUIDL AI: Unlocking the Infinite Potential of Hackathons
We refuse to let inefficiency limit innovation. BUIDL AI is our answer.
DoraHacks is launching BUIDL AI, the AI-powered Hackathon Co-Pilot that automates, scales, and supercharges hackathon organization.
BUIDL AI: The Game-Changing Features
1. Edit and Launch: One-Click Hackathon Deployment
Organizers can now launch a hackathon in minutes by filling in basic details (prizes, themes, workshops, judges, etc.). No tedious manual setup.
2. BUIDL Review: Submission Evaluation (10x Faster)
Traditional hackathons get hundreds of submissions—judging takes hundreds of hours. BUIDL AI changes the game. It automatically scores projects based on completeness, originality, and theme relevance—filtering out low-quality submissions 10x faster than before.
3. Automated Marketing: Instant Hackathon Reports
After the hackathon ends, BUIDL AI auto-generates a full post-event report—highlighting winners, standout projects, and key takeaways—boosting visibility and impact.
4. Seamless Interaction: Smarter Collaboration, No Bottlenecks
BUIDL AI will interact with hackathon organizers to keep organizers in sync, alerting them about new submissions, pending approvals, and participant inquiries in real time. No more dropped balls.
5. Multi-Hackathon Management: Scaling Innovation Without Limits
Before BUIDL AI, running multiple hackathons at once was a logistical nightmare. Now, ecosystem builders can launch and manage multiple hackathons seamlessly, boosting innovation frequency exponentially
The full BUIDL AI Beta version will release on April 15th, but multiple free BUIDL AI features have already been available on DoraHacks.io!
BUIDL AI: The Next Great Leap in Open Innovation
Hackathons aren’t just competitions. They are the birthplace of the next trillion-dollar innovations.
With BUIDL AI, hackathons enter a new era—automated, intelligent, and infinitely scalable. This means more hackers, more builders, and more breakthrough projects than ever before.
At DoraHacks, we believe in an open, hacker-driven future. BUIDL AI is the rocket fuel for that future.
-
 @ fd78c37f:a0ec0833
2025-03-18 10:44:40
@ fd78c37f:a0ec0833
2025-03-18 10:44:40In this edition, we’re thrilled to sit down with Tomek K from Bitcoin Alby, a passionate advocate for Bitcoin’s global adoption. Tomek K shares how Alby is driving innovation in the Bitcoin ecosystem and offers a glimpse into his vision for the cryptocurrency’s future. From his journey as a libertarian activist to co-founding the Bitcoin Film Festival, Tomek K’s story is one of curiosity, purpose, and a relentless pursuit of freedom through technology.
YakiHonne: Tomek K, it’s a pleasure to meet you! Today, we’re diving into your community topic—Alby Wallet. But before we begin, let me introduce our readers to Yakihonne. Yakihonne is a decentralized media client powered by the Nostr protocol, dedicated to promoting free speech through technology. It empowers creators to truly own their voices and assets, offering features like smart filtering, verified notes, and a focus on long-form content. So, Tomek, could you tell us about yourself and your work with Alby?
Tomek K: Of course! I’m Tomek K, originally from Poland, and right now, I’m speaking to you from Sri Lanka. I love traveling and observing how different countries adopt Bitcoin. For most of my career, I’ve been a free-market advocate, promoting economic freedom through various projects—essentially doing PR for capitalism. I’ve organized conferences, political demonstrations, economic seminars, summer festivals, and even opened a bar in Warsaw to spread these ideas in different ways.
During this advocacy work, I came across Bitcoin. At first, I didn’t pay much attention to it, but over time, I started feeling frustrated—our efforts raised awareness about freedom, but they didn’t bring measurable change. That led me to study Bitcoin more deeply, and I gradually shifted my focus to Bitcoin activism. Along the way, I collaborated with publishers to translate Bitcoin-related books into Polish and co-founded the Bitcoin Film Festival with friends from Meetup. Later, I joined Alby, marking my transition from free-market activism to Bitcoin promotion.
At the Bitcoin Film Festival, I handle operations and networking—organizing the event, managing logistics, and making things happen. Our team is small, but I enjoy the work. I’m passionate about Bitcoin because I came for the revolution, and I’m staying for the revolution.
That said, I don’t consider myself a Bitcoin absolutist. I see Bitcoin as a tool for freedom, not just a currency or a more efficient technology. If there were a better tool for advancing liberty and making societies freer, I’d probably focus on that. But for now, Bitcoin appears to be the most effective tool for freedom. Ultimately, I consider myself a “life maximalist”—because to live a good life, you need freedom, and to have freedom today, you need sound money. And right now, that money is Bitcoin.
YakiHonne: Was there a specific moment or event that sparked your interest in Bitcoin and motivated you to join the Alby community?
Tomek K: What attracted me to Bitcoin was its promise of global monetary independence and its ability to reduce the control of the Federal Reserve, central banks, and governments—the strongest and most covert control mechanisms in the world. Unfortunately, many people, even libertarians, often overlook this.
As for why I joined Alby, it’s because this startup is driven by values and mission rather than simply chasing profits, like selling tokens or games. This aligns well with my interest in the Lightning Network. As I explored Lightning more deeply, I came across Alby. I’ve always enjoyed testing new tools, trying them firsthand, and understanding the communities behind them—so naturally, I became part of it. Along the way, I also got to know some of the team members, which reinforced my involvement.
Additionally, Alby supported the Bitcoin Film Festival. While they weren’t the largest sponsor, their contribution was generous. The festival served as a great platform for them and other projects. I think it was good marketing because people like me—who have strong networking skills, arrange podcast interviews, and organize various activities—help build awareness and positive PR. That was part of my role.
If I had to pinpoint a single defining moment that led me here, I honestly couldn’t. Becoming a Bitcoiner doesn’t happen overnight. You can’t just read The Bitcoin Standard, declare that you understand Bitcoin, and instantly become a maximalist. Anyone who’s intellectually honest will admit that it takes multiple touchpoints—articles, films, career shifts, essays, hands-on experimentation, and actually using Bitcoin—to truly grasp its significance. I had many such moments along the way: reading The Bitcoin Standard, learning from friends who had a deeper understanding of Bitcoin, and working at Alby, which further expanded my knowledge of the Lightning Network’s capabilities and limitations. It wasn’t one turning point but a series of pivotal experiences that shaped my path.
YakiHonne: How did the Alby community start, and how did it attract its first members?
Tomek K: When I joined Alby, the community had already been established for some time. It originally emerged within the browser design community, where early users helped developers refine the product by providing feedback. That’s how the first members joined, and this process has been ongoing for four years now.
As for how Alby attracted members, it was through a mix of channels—social media (Twitter, Telegram, Discord), email engagement, and active participation in Bitcoin conferences. But the core strategy has always been openness, engaging with users, and listening to their feedback. Sometimes that means making a joke, sometimes defending against unfair criticism, and other times implementing requested features. We’ve always worked to maintain an active and friendly community atmosphere.
We also host bi-weekly community calls, which are a central part of our activities. Every two weeks, available team members meet with users for open Q&A sessions, issue discussions, and demonstrations of various projects integrating with Alby. I’ve participated in some of these calls, and they help maintain strong relationships with users, developers, and other projects—something crucial for the ecosystem. The Bitcoin technology landscape is somewhat fragmented, and grassroots coordination is necessary since there’s no single leader defining terminology or coding practices.
That’s also why Alby doesn’t exist in isolation. Almost everything we’ve built has been made possible by the creators of previous libraries, prior codebases, and collaborative efforts in writing specifications for protocols. Projects like Yakihonne and many others also recognize the importance of open-source collaboration. I think it’s essential to acknowledge the contributions of the open-source community. One thing I really appreciate is that Bitcoiners are driving open-source development in virtually every part of the world, all working toward a shared and meaningful goal.
YakiHonne:Were there any notable challenges in the early days that left a strong impression on you?
Tomek K :When I first joined Alby, I struggled with a bit of imposter syndrome for months. I was handling PR for the project, but I didn’t fully understand all the technical details—how certain protocols interact or what’s happening under the hood. It took time to get familiar with everything and really feel like I belonged.
Regulatory pressure has also been a huge challenge. In some cases, developers have been arrested, projects have had to leave certain countries, and users have been geoblocked based on their location. But challenges like these can also drive innovation. For example, Alby developed AlbyHub, an open-source self-custodial node, as a response to these kinds of issues.
There are always risks in this space—governments might suddenly demand a banking license or require compliance with new regulations. These are real obstacles, but we tackle them by embracing decentralization and open-source solutions. That’s how we ensure the project stays true to its mission and vision.

YakiHonne:If someone wanted to start a Bitcoin community today or grow an existing one, what advice would you give them?
Tomek K: The most important thing is to just get started. A community begins with action, and it takes more than one person. Even if it’s just you and a friend grabbing a beer, that’s already a start. Maybe after the first or second meetup, you post on Meetup.com, Twitter, or local forums:"Hey, we’re hosting a Bitcoin meetup in this city. We just want to connect with other Bitcoiners!" If you keep doing it consistently, the community will naturally grow. Over time, the bar where you meet might get interested in accepting Bitcoin, or you might meet some OGs in your area who decide to join—maybe they already run a business and want to support what you’re doing.
You don’t have to over-plan everything from the start. No need to think, “We need a podcast, 10 episodes, a logo…”—all that can come later. Just bootstrap it: organize a meetup, grab a beer, and get going. As you go, you’ll adapt, improve, and build recognition.Beyond that, it’s a great way to meet other Bitcoiners, develop leadership skills, and learn about community building. And at the very least, you’ll have fun doing it—which, honestly, is one of the main reasons I keep organizing meetups and other activities.
YakiHonne: Exactly, the key is to take action—just start and see where it leads. Does your community focus more on Bitcoin’s technical aspects, like coding and development, or do you emphasize non-technical areas such as education and outreach? Or do you try to balance both?
Tomek K: Our users come from all kinds of backgrounds. Some are very engaged and provide feedback regularly, while others prefer to stay in the background. Some attend our community calls, and within that group, some are developers actively building projects and collaborating with us. At the same time, there are developers we know are out there, but they never directly engage with us. That’s just how the Bitcoin community works—there’s no strict definition of being part of Alby. People engage in their own way. Some users are active on Discord, some aren’t, but we treat them all as part of the family, keeping them informed through newsletters, offering support, and making sure they stay updated with what’s happening at Alby.
As for whether we lean more toward technical development or non-technical outreach, there’s no clear-cut answer. Our community is diverse—we cater to a wide range of Lightning Network users. Some just use the browser extension, while others are deeply involved in our ecosystem. We also work with NGOs, educational initiatives, and community organizations. At the same time, we place a strong emphasis on developers and maintaining good relationships with them. Our repositories and developer portal offer useful libraries and examples, making it easier for both aspiring and experienced developers to integrate the Lightning Network into their projects. Developer relations are something we consider highly important.

YakiHonne: I understand that you're also the founder of another Bitcoin-related film project. Could you tell us a bit about it? What exactly inspired you to combine Bitcoin and filmmaking?
Tomek K: Yes, I founded Bitcoin Film Fest to help build what I call Bitcoin Cinema—an emerging industry that blends Bitcoin and filmmaking. I wanted to track everything happening at the intersection of these two worlds. Just like e-commerce, energy, and information technology, I believe the film industry will eventually be shaped by Bitcoin. And in fact, it’s already happening. There are Bitcoin-themed movies, and even major Hollywood productions have started including Bitcoin references. Bitcoin filmmakers, Bitcoin culture, and even a Bitcoin subculture already exist. We have our own heroes, stories, and values, and from this, films are being created. I love cinema, and I love Bitcoin—this was my way of bringing the two together.
The festival itself happened somewhat by accident—but maybe it was meant to be. It all started in Warsaw when I was organizing a Bitcoin meetup. I planned to screen a Bitcoin documentary, but due to technical issues, it didn’t happen. So, over a few beers, we came up with an idea: if we couldn’t show one film, why not go all in and create a full-scale Bitcoin film festival? We started researching and realized there were enough Bitcoin-related films out there to make it happen. So, we did.
The response from the community was overwhelmingly positive. It became clear that people wanted a space for Bitcoin cinema—a hub for information, networking, and collaboration. We started using the term “Binema” (Bitcoin Cinema) to describe this emerging genre. I find it fascinating to witness the growth of Bitcoin culture and storytelling. Before this, I had followed libertarian artistic movements closely, and now I see how important culture is for Bitcoin’s adoption—it’s not just about the technical and financial aspects.
Bitcoin adoption isn’t going to happen overnight, and it won’t happen without developers, educators, infrastructure builders, UX designers, and many others contributing to the ecosystem. Culture is one of the most powerful tools for shaping society, and I, like many others, am working to bring Bitcoin adoption closer through film. We’re witnessing the early days of Bitcoin cinema. I missed out on the birth of traditional cinema, but this time, I want to be part of it.
YakiHonne:In your region, does the government support or oppose Bitcoin? How has this stance impacted the development of the Bitcoin community so far?
Tomek K :Bitcoin doesn’t concern itself with nation-state borders, and frankly, we don’t either. The situation in Poland has little influence on what we do. The only connection is that I, along with two others, happen to be in Poland, but most of our team is globally distributed. On a broader scale, the U.S. tends to shape regulatory trends, and unfortunately, it often does so in a more restrictive way. However, Poland itself hasn’t had a significant impact on our work.
YakiHonne:Has your Bitcoin Film Fest community ever used film as a way to connect with members—perhaps by watching a Bitcoin-related movie or hosting a movie night to make things more fun and engaging? Have you done anything like that before?
Tomek K:Yes, absolutely! The film festival itself is a great example—we watch movies together and build a community around them. Aside from the festival we organized in Warsaw, we've also hosted film screenings at various Bitcoin events, like Sats and Facts in Thailand, BTC Prague, Plan B Lugano, Frimadera, Adopting Bitcoin, and several other conferences. We also organize online watch parties—actually, there's one happening next Sunday. The movie is available on Prime Video, but we'll sync up on Discord to watch it together, chat, and share our thoughts. We'll be announcing it on Twitter, so if you check Bitcoin Film Fest on Twitter, you'll find details on how to join.
Film has been a great way to connect with members and spark discussions. We've seen Bitcoin meetups worldwide organizing movie nights—our volunteer friends in Montenegro have hosted one, and our partners in Kenya and South Africa have done the same. Lately, movie nights have been happening more and more frequently, which is exciting.
It's still early—after all, Bitcoin is only 16 years old, so the selection of Bitcoin movies is still relatively small. Many of these films haven’t had large budgets or massive talent pools yet, but that’s changing. Right now, we’re primarily focused on showing films within the Bitcoin community rather than creating films aimed at the general public. That said, those kinds of projects are also emerging. I’m optimistic about the growth of Bitcoin cinema—better storytelling, AI-driven advancements, increasing interest from audiences, and even sponsors willing to invest in filmmakers. Big things are coming, and while we already have some great Bitcoin films, the best is yet to come. We’re still in the early days, and this is the time to contribute and help shape the future of Bitcoin cinema.
YakiHonne:We’ve come to the end of today’s interview, and I’ve truly enjoyed every moment of it. I’m very sure your idea will be incredibly engaging, inspiring more people and attracting a broad audience. Thank you so much for your time today—it was a great conversation.
-
 @ 75869cfa:76819987
2025-03-18 07:54:38
@ 75869cfa:76819987
2025-03-18 07:54:38GM, Nostriches!
The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review:
In the past two weeks, Nostr statistics indicate over 225,000 daily trusted pubkey events. The number of new users has seen a notable decrease, with profiles containing a contact list dropping by 95%. More than 10 million events have been published, with posts and reposts showing a decrease. Total Zap activity stands at approximately 15 million, marking a 10% decrease.
Additionally, 26 pull requests were submitted to the Nostr protocol, with 6 merged. A total of 45 Nostr projects were tracked, with 8 releasing product updates, and over 463 long-form articles were published, 29% focusing on Bitcoin and Nostr. During this period, 2 notable events took place, and 3 significant events are upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 225,000, representing a slight 8 % decrease compared to the previous period. Daily activity peaked at 18179 events, with a low of approximately 16093.
The number of new users has decreased significantly. Profiles with a contact list are now around 17,511, reflecting a 95% drop. Profiles with a bio have decreased by 62% compared to the previous period. The only category showing growth is pubkeys writing events, which have increased by 27%.
Regarding event publishing, all metrics have shown a decline. The total number of note events published is around 10 million, reflecting a 14% decrease. Posts remain the most dominant in terms of volume, totaling approximately 1.6 million, which is a 6.1% decrease. Both reposts and reactions have decreased by about 10%.
For zap activity, the total zap amount is about 15 million, showing an increase of over 10% compared to the previous period.
Data source: https://stats.nostr.band/
NIPs
nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z is proposing that A bulletin board is a relay-centric system of forums where users can post and reply to others, typically around a specific community. The relay operator controls and moderates who can post and view content. A board is defined by kind:30890. Its naddr representation must provide the community's home relays, from which all posts should be gathered. No other relays should be used.
nostr:npub1xy54p83r6wnpyhs52xjeztd7qyyeu9ghymz8v66yu8kt3jzx75rqhf3urc is proposing a standardized way to represent fitness and workout data in Nostr, including: Exercise Templates (kind: 33401) for storing reusable exercise definitions, Workout Templates (kind: 33402) for defining workout plans, Workout Records (kind: 1301) for recording completed workouts. The format provides structured data for fitness tracking while following Nostr conventions for data representation.Many fitness applications use proprietary formats, locking user data into specific platforms. This NIP enables decentralized fitness tracking, allowing users to control their workout data and history while facilitating social sharing and integration between fitness applications.
nostr:npub1zk6u7mxlflguqteghn8q7xtu47hyerruv6379c36l8lxzzr4x90q0gl6ef is proposing a PR introduces two "1-click" connection flows for setting up initial NWC connections. Rather than having to copy-paste a connection string, the user is presented with an authorization page which they can approve or decline. The secret is generated locally and never leaves the client. HTTP flow - for publicly accessible lightning wallets. Implemented in Alby Hub (my.albyhub.com) and CoinOS (coinos.io). Nostr flow - for mobile-based / self-hosted lightning wallets, very similar to NWA but without a new event type added. Implemented in Alby Go and Alby Hub. Benefits over NWC Deep Links are that it works cross-device, mobile to web, and the client-generated secret never leaves the client. Both flows are also implemented in Alby JS SDK and Bitcoin Connect.
add B0 NIP for Blossom interaction
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 describes a tiny subset of possible Blossom capabilities, but arguably the most important from the point of view of a most basic Nostr client. This NIP specifies how Nostr clients can use Blossom for handling media. Blossom is a set of standards (called BUDs) for dealing with servers that store files addressable by their SHA-256 sums. Nostr clients may make use of all the BUDs for allowing users to upload files, manage their own files and so on, but most importantly Nostr clients SHOULD make use of BUD-03 to fetch kind:10063 lists of servers for each user.
nostr:npub149p5act9a5qm9p47elp8w8h3wpwn2d7s2xecw2ygnrxqp4wgsklq9g722q defines a standard for creating, managing and publishing to communities by leveraging existing key pairs and relays, introducing the concept of "Communi-keys". This approach allows any existing npub to become a community (identity + manager) while maintaining compatibility with existing relay infrastructure.
A way for relays to be honest about their algos
securitybrahh is proposing a PR introduces NIP-41, a way for relays to be honest about their algos, edits 01.md to account for changes in limit (related #78, #1434, received_at?, #620, #1645) when algo is provided, appends 11.md for relays to advertize whether they are an aggregator or not and their provided algos. solves #522, supersedes #579.
nip31: template-based "alt" tags for known kinds
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 is proposing that clients hardcoding alt tags are not very trustworthy. alt tags tend to be garbage in a long-enough timeframe.This fixes it with hardcoded rich templates that anyone can implement very easily without having to do it manually for each kind. alt tags can still be used as a fallback.
nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z is proposing a PR addresses 3 main problems of NIP-44v2. First, It has a message size limit of 65Kb, which is unnecessarily small. Second, It forces the encrypting key to be the same as the event's signing key. Which forces multi-sig actors to share their main private key in order to encrypt the payload that would be later signed by the group. Decoupling singing and encryption keys, for both source and destination, is one of the goals of this version. And It offers no way to describe what's inside the encrypted blob before requesting the user's approval to decrypt and send the decrypted info back to the requesting application. This PR adds an alt description to allow decrypting signers to display a message and warn the user of what type of information the requesting application is receiving.
Notable Projects
Damus nostr:npub18m76awca3y37hkvuneavuw6pjj4525fw90necxmadrvjg0sdy6qsngq955
- Notes in progress will always be persisted and saved automatically. Never lose those banger notes when you aren't quite ready to ship them.
- Make your profile look just right without any fuss. It also optimizes them on upload now to not nuke other people’s phone data bills.
- You won't see the same note more than once in your home feed.
- Fixed note loading when clicking notifications and damus.io links.
- Fixed NWC not working when you first connect a wallet.
- Fixed overly sensitive and mildly infuriating touch gestures in the thread view when scrolling
Primal nostr:npub12vkcxr0luzwp8e673v29eqjhrr7p9vqq8asav85swaepclllj09sylpugg
Primal for Android build 2.1.9 has been released. * Multi-account support * Deep linking support * "Share via Primal" support * Bug fixes and improvements
Yakihonne nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
YakiHonne Wallet just got a fresh new look!
0xchat nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72
0xchat v1.4.7-beta release * Upgraded the Flutter framework to v3.29.0. * Private chat implementation changed to NIP-104 Nostr MLS. * NIP-17 and NIP-29 messages now support q tags. * You can swipe left to reply to your own messages. * Chat messages now support code block display. * Copy images from the clipboard. * Fixed an issue where underlined text in chat appeared as italic.
GOSSIP 0.14.0 nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8
Several major bugs have been fixed in the last week. * New Features and Improvements * Zappers and amounts are now shown (click on the zap total) * Reactions and who reacted are now shown (click on the reaction numbers) * Multiple search UI/UX improvements * Undo Send works for DMs too * Undo Send now restores the draft * UI: Side panel contains less so it can be thinner. Bottom bar added. * UI: frame count and spinner (optional) * Relay UI: sorting by score puts important relays at the top. * Relay UI: add more filters so all the bits are covered * Image and video loading is much faster (significant lag reduction) * Thread loading fix makes threads load far more reliably * Settings have reset-to-default buttons, so you don't get too lost. * Setting 'limit inbox seeking to inbox relays' may help avoid spam at the expense of possibly * Fix some bugs * And more updates
Nostur v1.18.1 nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0
New in this version: * Floating mini video player * Videos: Save to library, Copy video URL, Add bookmark * Improved video stream / chat view * Top zaps on live chat * Posting to Picture-first * Profile view: Show interactions with you (conversations, reactions, zaps, reposts) * Profile view: Show actual reactions instead of only Likes * Improved search + Bookmark search * Detect nsfw / content-warning in posts * Show more to show reactions outside Web of Trust * Show more to show zaps outside Web of Trust * Support .avif image format * Support .mp3 format * Support .m4v video format * Improved zap verification for changed wallets * Improved outbox support * Show label on restricted posts * Low data mode: load media in app on tap instead of external browser * Many other bug fixes and performance improvements
Alby nostr:npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm
Latest two releases of Alby Go, 1.10 and 1.11, brought you lots of goodies: * BTC Map integration for quick access to global bitcoin merchants map * Confirm new NWC connections to your Alby Hub directly in Alby Go! No more copy-pasting or QR code scanning * Support for MoneyBadger Pay Pick n Pay QR payments in over 2000 stores in South Africa
ZEUS v0.10.0 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5
ZEUS v0.10.0 is now available. This release features the ability to renew channel leases, spin up multiple embedded wallets, Nostr Wallet Connect client support, and more. * Renewable channels * NWC client support * Ability to create multiple Embedded LND 'node in the phone' wallets * Ability to delete Embedded LND wallets * Embedded LND: v0.18.5-beta * New share button (share ZEUS QR images) * Tools: Export Activity CSVs, Developer tools, chantools * Activity: filter by max amount, memo, and note
Long-Form Content Eco
In the past two weeks, more than 463 long-form articles have been published, including over 91 articles on Bitcoin and more than 41 related to Nostr, accounting for 29% of the total content.
These articles about Nostr mainly explore the rise of Nostr as a decentralized platform that is reshaping the future of the internet. They emphasize Nostr's role in providing users with greater freedom, ownership, and fair monetization, particularly in the realm of content creation. The platform is positioned as a counter to centralized social media networks, offering uncensored interactions, enhanced privacy, and direct transactions. Many articles delve into Nostr’s potential to integrate with Bitcoin, creating a Layer 3 solution that promises to end the dominance of old internet structures. Discussions also cover the technical aspects of Nostr, such as the implementation of relays and group functionalities, as well as security concerns like account hacks. Furthermore, there is an exploration of the philosophical and anthropological dimensions of Nostr, with the rise of "Dark Nostr" being portrayed as a deeper expression of decentralized freedom.
The Bitcoin articles discuss the ongoing evolution of Bitcoin and its increasing integration into global financial systems. Many articles focus on the growing adoption of Bitcoin, particularly in areas like Argentina and the U.S., where Bitcoin is being used for rental payments and the establishment of a strategic Bitcoin reserve. Bitcoin is also portrayed as a response to the centralized financial system, with discussions about how it can empower individuals through financial sovereignty, provide a hedge against inflation, and create fairer monetization models for creators. Additionally, the articles explore the challenges and opportunities within the Bitcoin ecosystem, including the rise of Bitcoin ETFs, the development of Bitcoin mining, and the potential impact of AI on Bitcoin adoption. There is also emphasis on Bitcoin's cultural and economic implications, as well as the need for decentralized education and innovation to drive further adoption.
Thank you, nostr:npub1ygzsm5m9ndtgch9n22cwsx2clwvxhk2pqvdfp36t5lmdyjqvz84qkca2m5 nostr:npub1rsv7kx5avkmq74p85v878e9d5g3w626343xhyg76z5ctfc30kz7q9u4dke nostr:npub17wrn0xxg0hfq7734cfm7gkyx3u82yfrqcdpperzzfqxrjf9n7tes6ra78k nostr:npub1fxq5crl52mre7luhl8uqsa639p50853r3dtl0j0wwvyfkuk4f6ssc5tahv nostr:npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx nostr:npub19mf4jm44umnup4he4cdqrjk3us966qhdnc3zrlpjx93y4x95e3uq9qkfu2 nostr:npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0 nostr:npub1uv0m8xc6q4cnj2p0tewmcgkyzg8cnteyhed0zv30ez03w6dzwvnqtu6gwl nostr:npub1ygzsm5m9ndtgch9n22cwsx2clwvxhk2pqvdfp36t5lmdyjqvz84qkca2m5 nostr:npub1mhcr4j594hsrnen594d7700n2t03n8gdx83zhxzculk6sh9nhwlq7uc226 nostr:npub1xzuej94pvqzwy0ynemeq6phct96wjpplaz9urd7y2q8ck0xxu0lqartaqn nostr:npub1gqgpfv65dz8whvyup942daagsmwauj0d8gtxv9kpfvgxzkw4ga4s4w9awr nostr:npub16dswlmzpcys0axfm8kvysclaqhl5zv20ueurrygpnnm7k9ys0d0s2v653f and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.
Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries. * The first Bitcoin Meetup organized by Mi Primer Bitcoin was successfully held on March 14, 2025, at Texijal Pizza in Apaneca. The event included Bitcoin education, networking, a Q&A session, and merchandise distribution, offering an exciting experience for all participants.
* The Btrust Space discussion was successfully held on March 13, 2024. The event focused on how to support Bitcoin developers, fund open-source contributions, and grow the Bitcoin ecosystem. The speakers included Bitcoin core contributors, Btrust CEO, engineering leads, and other project leaders.Here is the upcoming Nostr event that you might want to check out.
- The Nostr Workshop, organized by YakiHonne and Bitcoin Safari, will take place online via Google Meet on March 17, 2025, at 7:00 PM (GMT+1). The event will introduce the Nostr ecosystem and Bitcoin payments, with participants learning about decentralized technology through YakiHonne and earning rewards. Register and verify your account to claim exclusive rewards, and invite friends to unlock additional rewards.
- The 2025 Bitcoin, Crypto Economy, and Law FAQ Webinar will be held online on March 20, 2025 (Thursday) from 12:00 to 13:00 Argentina time. The webinar will be hosted by Martin Paolantonio (Academic Director of the course) and Daniel Rybnik (Lawyer specializing in Banking, Corporate, and Financial Law). The session aims to introduce the academic program and explore Bitcoin, the crypto economy, and related legal issues.
- Bitcoin Educators Unconference 2025 will take place on April 10, 2025, at Bitcoin Park in Nashville, Tennessee, USA. This event is non-sponsored and follows an Unconference format, allowing all participants to apply as speakers and share their Bitcoin education experiences in a free and interactive environment. The event has open-sourced all its blueprints and Standard Operating Procedures (SOPs) to encourage global communities to organize similar Unconference events.
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
 @ edf0da8b:b2652fa3
2025-03-17 17:28:33
@ edf0da8b:b2652fa3
2025-03-17 17:28:33One remarkable thing the Wim Hof Method stirs in me is that I increasingly feel the desire to connect with pure nature. Now, what does that mean?
You may know that slight feeling of eeriness when looking at deep moving waters or that tiny insecurity when darkness creeps up around you alone among the trees? You are sure there's nothing to worry about. But still, these little old conditioned anxieties, these unreasonable mind scenarios, they keep coming up and make you seek safety.
They are different for everyone, but these anxieties in the foreground are a sign for inner blockages that deprive us from expressing our power and creativity. What's more, they separate us from nature. They suggest, everything around us is potentially dangerous. Is it though?
When practicing the Wim Hof Method, and especially right after the breathing exercises, I can immediately feel a clarity emerging, a stronger awareness of presence in the moment. Anxieties are caringly pushed back to their rightful place, but do not control my actions and no longer dominate my state of being.
And so suddenly, the world view shifts. Eerie deep moving waters become fascinating, the darkness around reveals the beauty of trees casting soft moonlight shadows. I deeply appreciate what is, I want to touch the waters, I want to merge with the shadows, I feel that power. Instead of running away I want to connect with nature. I'm more aware of the present and should danger reveal itself, I have the confidence that I can properly react when it arises. But until then, I can enjoy beauty and connectedness. The powerful shift is from scenarios about potential threats around me to curiosity and beautiful opportunity everywhere.
There are countless great techniques and traditions that guide us to such shifts. But with regular practice, I find the Wim Hof Method to be particularly simple, accessible and effective.
wimhofmethod
-
 @ 401014b3:59d5476b
2025-03-27 13:48:10
@ 401014b3:59d5476b
2025-03-27 13:48:10Alright, baseball junkies, it’s March 27, 2025, and we’re diving into the crystal ball to predict the 2025 MLB season—straight through to the World Series champ! Spring Training’s wrapping up, Opening Day’s here, and the league’s loaded with talent, drama, and some sneaky contenders ready to shake things up. I’m breaking down each playoff team’s path, their strengths, weaknesses, and who’s got the juice to hoist the trophy in October. This ain’t some cookie-cutter chalk pick—let’s get gritty, let’s get bold, and let’s see who’s got the stones to win it all. Strap in, fam—here we go!
American League Playoff Teams: The AL Beast Mode
New York Yankees\ The Yankees are back, and they’re pissed after last year’s World Series loss to the Dodgers. Aaron Judge is coming off another MVP-caliber season (let’s say .310, 55 HRs, 130 RBIs), and Juan Soto’s bat (projected .290, 40 HRs) gives them a lethal 1-2 punch. Gerrit Cole anchors a rotation that’s top-5 in ERA (around 3.40), but the bullpen’s a question mark—closer Clay Holmes blew 13 saves in 2024, and they haven’t fixed that yet. They’ll win the AL East (95-67), but their postseason hinges on late-inning reliability.\ Prediction: ALCS run, but they fall short if the pen implodes.
Houston Astros\ The Astros are perennial AL West champs (projected 92-70), even with a slightly aging core. Jose Altuve (.300, 20 HRs) and Yordan Alvarez (.295, 35 HRs) keep the offense humming, and a rotation led by Framber Valdez (3.20 ERA) and Hunter Brown (3.50 ERA) is solid. Their bullpen, with Josh Hader (1.28 ERA in 2024), is lights-out. But injuries to key arms like Justin Verlander (aging at 42) could bite them.\ Prediction: ALDS exit—they’re good, but not great this year.
Cleveland Guardians\ The Guardians sneak into the playoffs as the AL Central champs (88-74). Jose Ramirez (.280, 35 HRs, 110 RBIs) is a one-man wrecking crew, and their rotation—Shane Bieber (3.00 ERA, if healthy) and Triston McKenzie (3.60 ERA)—keeps them in games. But their offense outside Ramirez is thin (team OPS around .720), and the bullpen’s inconsistent (4.00 ERA).\ Prediction: Wild Card exit—they’re scrappy but lack firepower.
Tampa Bay Rays (Wild Card)\ The Rays grab a Wild Card spot (90-72) with their usual mix of grit and analytics. Yandy Diaz (.290, 15 HRs) and Randy Arozarena (.270, 25 HRs) lead a balanced offense, while Shane McClanahan (3.10 ERA) and Zach Eflin (3.40 ERA) anchor the rotation. Their bullpen (top-10 in ERA at 3.50) is a strength, but depth issues (injuries to key prospects) could hurt.\ Prediction: ALDS run—they’re sneaky dangerous.
Seattle Mariners (Wild Card)\ The Mariners finally break through as a Wild Card (89-73), as predicted by some fans on X. Julio Rodriguez (.285, 30 HRs) and Cal Raleigh (.250, 35 HRs) power the offense, and a rotation of Luis Castillo (3.20 ERA), Logan Gilbert (3.30 ERA), and George Kirby (3.40 ERA) is the best in the AL (team ERA around 3.20). Their offense (bottom-10 in runs scored) is the Achilles’ heel.\ Prediction: ALCS run—they’re a pitcher’s dream, but the bats hold ‘em back.
Baltimore Orioles (Wild Card)\ The Orioles snag a Wild Card (87-75), but some fans on X call them a “surprise disappointment.” Gunnar Henderson (.280, 35 HRs) and Adley Rutschman (.270, 20 HRs) lead a young core, but the rotation—Corbin Burnes (3.00 ERA) and Grayson Rodriguez (3.70 ERA)—lacks depth after losing Kyle Bradish to injury. The bullpen (4.20 ERA) is shaky.\ Prediction: Wild Card exit—too many holes this year.
National League Playoff Teams: The NL Wild West
Los Angeles Dodgers\ The Dodgers are the NL West juggernaut (98-64), and some fans on X are already calling them World Series champs. Shohei Ohtani (.300, 50 HRs, 120 RBIs) is the NL MVP favorite, Mookie Betts (.290, 30 HRs) is elite, and Freddie Freeman (.310, 25 HRs) is steady. The rotation—Tyler Glasnow (3.10 ERA), Yoshinobu Yamamoto (3.30 ERA), and Walker Buehler (3.50 ERA)—is deep, and the bullpen (3.40 ERA) is solid. No weaknesses here.\ Prediction: World Series bound—they’re a machine.
Philadelphia Phillies\ The Phillies win the NL East (94-68) with a balanced attack. Bryce Harper (.290, 30 HRs) and Kyle Schwarber (.250, 40 HRs) mash, while Trea Turner (.300, 20 HRs) adds speed. The rotation—Zack Wheeler (3.00 ERA), Aaron Nola (3.40 ERA), and Ranger Suarez (3.60 ERA)—is top-tier, and the bullpen (3.50 ERA) is reliable. They’re built for October.\ Prediction: NLCS run—they’re legit contenders.
Milwaukee Brewers\ The Brewers take the NL Central (90-72) with a scrappy squad. Willy Adames (.270, 30 HRs) and William Contreras (.280, 20 HRs) lead the offense, while Freddy Peralta (3.30 ERA) and Brandon Woodruff (3.50 ERA, if healthy) anchor the rotation. Their bullpen (top-5 in ERA at 3.30) is a strength, but the offense (middle-of-the-pack in runs) can stall.\ Prediction: NLDS exit—not enough firepower.
Atlanta Braves (Wild Card)\ The Braves grab a Wild Card (91-71) despite injuries. Ronald Acuna Jr. (.290, 35 HRs) and Matt Olson (.270, 40 HRs) power the lineup, but the rotation—Chris Sale (3.20 ERA) and Max Fried (3.40 ERA)—is thin after Spencer Strider’s injury. The bullpen (3.60 ERA) is solid, but depth is a concern.\ Prediction: NLDS run—they’re talented but banged up.
San Diego Padres (Wild Card)\ The Padres snag a Wild Card (89-73) with a balanced attack. Fernando Tatis Jr. (.280, 35 HRs) and Manny Machado (.270, 30 HRs) lead the offense, while Dylan Cease (3.30 ERA) and Yu Darvish (3.50 ERA) anchor the rotation. The bullpen (3.70 ERA) is decent, but they lack a true closer.\ Prediction: Wild Card exit—not enough late-game juice.
New York Mets (Wild Card)\ The Mets sneak in as a Wild Card (88-74) with a breakout year. Francisco Lindor (.280, 30 HRs) and Pete Alonso (.260, 35 HRs) mash, while Kodai Senga (3.20 ERA) and Luis Severino (3.60 ERA) lead the rotation. The bullpen (4.00 ERA) is a weak spot, but their offense (top-10 in runs) keeps ‘em alive.\ Prediction: NLDS run—they’re scrappy but flawed.
Playoff Breakdown: The Road to the World Series
AL Wild Card:
- Rays over Guardians
- Mariners over Orioles
- Yankees over Rays
- Mariners over Astros
- Yankees vs. Mariners → Yankees (4-2)\ Judge and Soto go off, and the Mariners’ bats can’t keep up with New York’s firepower. Cole’s ace stuff seals it.
NL Wild Card:
- Braves over Padres
- Mets over Brewers
- Dodgers over Mets
- Phillies over Braves
- Dodgers vs. Phillies → Dodgers (4-3)\ Ohtani’s heroics (think a 3-HR game) and the Dodgers’ depth outlast Philly’s grit in a seven-game classic.
World Series: Yankees vs. Dodgers
Here we go—a rematch of last year’s epic clash! The Yankees are hungry for revenge, with Judge and Soto swinging for the fences (combined 5 HRs in the series). Cole (Game 1 gem, 7 IP, 2 ER) and Rodon (Game 5 win) keep it close, but the Dodgers’ lineup is relentless—Ohtani (.350, 2 HRs), Betts (.320, 3 doubles), and Freeman (.300, 8 RBIs) overwhelm New York’s shaky bullpen. Glasnow and Yamamoto each win a start, and the Dodgers’ pen (2.50 ERA in the series) slams the door. Dodgers win in 6—Ohtani’s walk-off in Game 6 seals it.
The Final Buzzer
The Dodgers are my 2025 World Series champs—they’ve got the star power, depth, and clutch factor to repeat. The Yankees make a valiant run, but their bullpen woes bite ‘em again. Hit me on X if you disagree, but this is my October gospel—let’s see who’s standing when the dust settles! Play ball, degenerates!
-
 @ 06bc9ab7:427c48f5
2025-03-17 15:46:23
@ 06bc9ab7:427c48f5
2025-03-17 15:46:23Bitcoin Safe - A bitcoin savings wallet for the entire family
Designed for both beginners and power users, Bitcoin Safe combines security with an intuitive user experience. In this article, we dive deep into its features, unique benefits, and the powerful tools that make managing your Bitcoin wallet simple and secure.
Built for Learners
✔️ Step-by-step wallet setup wizard + PDF backup sheets 📄 🧪 Test transactions to ensure all hardware signers are ready 🔑 🛡️ Secure: Hardware signers only – no hot wallet risks 🚫🔥 🌍 Multi-language support: 🇺🇸 🇨🇳 🇪🇸 🇯🇵 🇷🇺 🇵🇹 🇮🇳 🇮🇹 🇫🇷 🇩🇪 🇲🇲 🇰🇷 📁 Address categories for easy organization ☁️ Label and category synchronization, and cloud backup (optional) 💰 Automatic UTXO merging to save on fees ⚡ Fast syncing with Electrum servers, Compact Block Filters coming soon
Built for Power Users
🔐 Supports Coldcard, Bitbox02, Jade, Trezor, Passport, Keystone & many more 🏦 💬 Multi-party multisig chat & PSBT sharing (optional) 📊 Transaction flow diagrams to trace coin movements 🔍 Instant cross-wallet wallet search ⚙️ Set your own electrum server, mempool instance, and nostr relay
Step-by-Step Wallet Setup
Whether you’re setting up a single-signature or multi-signature wallet, the setup wizard guides you every step of the way:

- Single Sig Wizard: Follow the intuitive wizard that walks you through each step. https://youtu.be/m0g6ytYTy0w
Clear instructions paired with hardware signer screen-shots, like the steps for a Coldcard
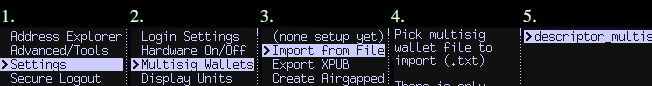
-
Multisig Wizard: The wizard ensures you do all necessary steps for a Multisig wallet in the right order. Afterwards your Multisig is ready to use and all signers are tested. Check out https://bitcoin-safe.org/en/features/setup-multisignature-wallet/
-
PDF Backup: The wizard will also generates 3 PDF backup sheets for a 2-of-3 multisig wallet, so ensure you always have your wallet descriptor together with the seed.
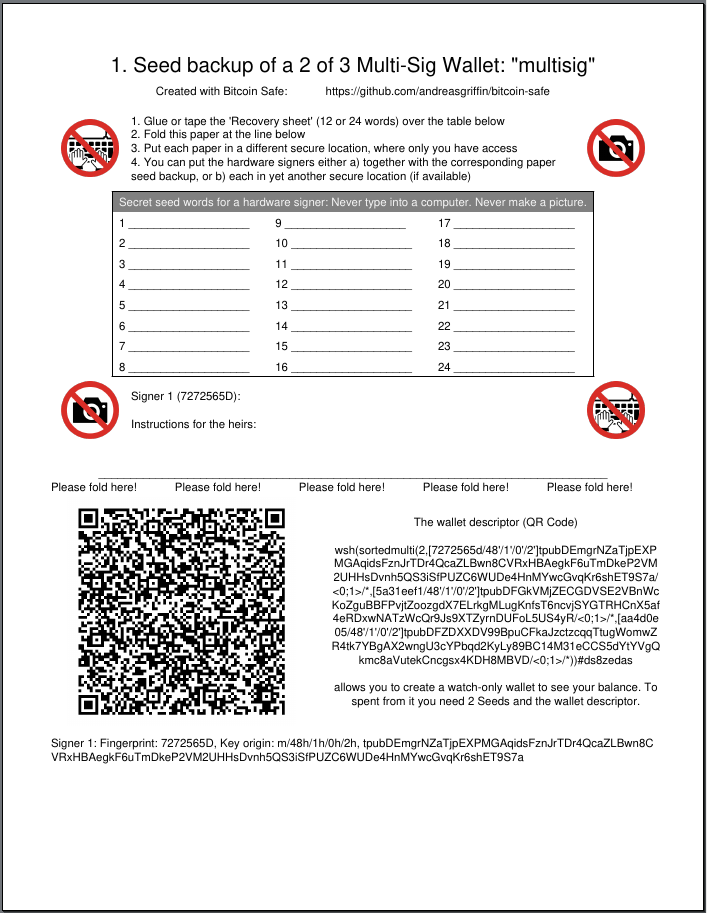
-
Hardware Signer Support: With full support for major hardware signers your keys remain securely offline.
Transaction Visualization
Visualize and navigate your transaction history:
-
Graphical Explorer: An interactive transaction diagram lets you click on inputs and outputs to follow the money flow intuitively.
-
Coin Categories: Organize your addresses into distinct coin categories (e.g., “KYC”, “Work”, “Friends”) so Bitcoin Safe automatically selects the correct inputs when creating PSBTs.

It prevents you accidentally linking coin categories when creating a transaction, and warns you if mistakes happened in the past.
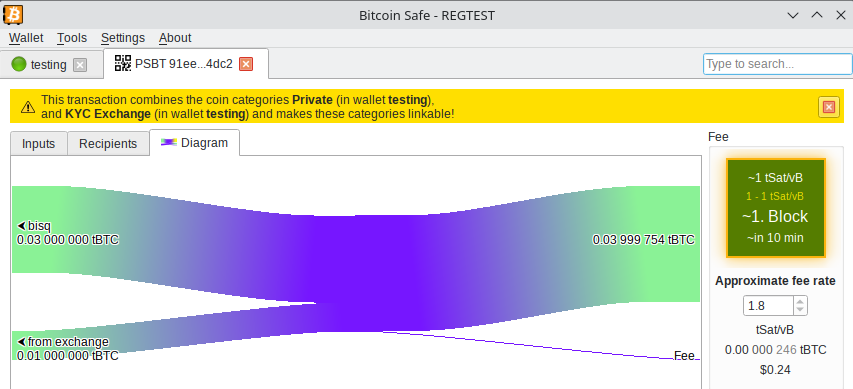
Powerful Wallet Management Tools
- Flexible Fee Selection: Choose fees with one click using an intuitive mempool block preview.
- UTXO Management: Automatically (optional) merge UTXOs when fees are low.
- CSV Table Export: Right click, Drag&Drop, or CTRL+C for immediate CSV export for easy processing in Excel.
- PDF Balance Statement: Export the address balances for easy record keeping on paper.
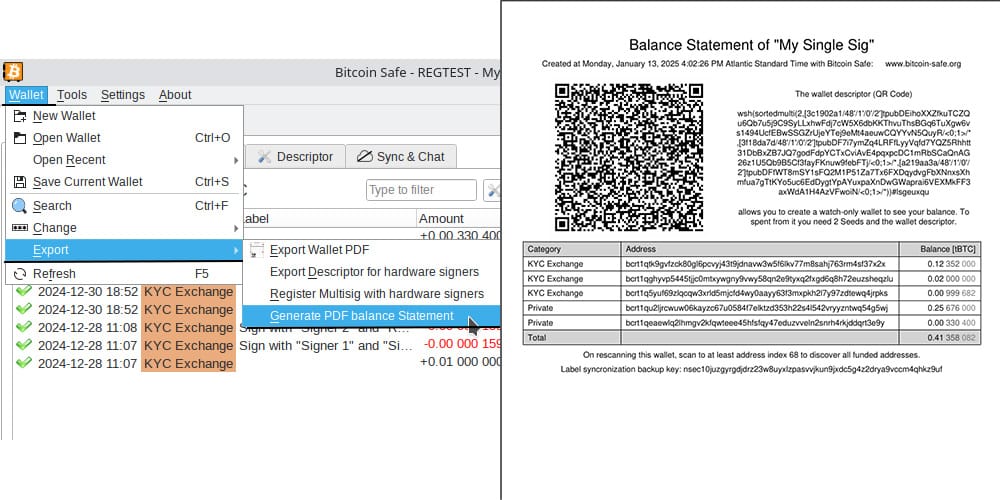
Advanced Features for the Power-User
Sync & Chat is off by default (for the paranoid user), but can be enabled with just one click.
Label Synchronization and Backup
- Seamless Sync: Using encrypted nostr messages, Bitcoin Safe synchronizes your coin categories and labels across multiple devices.
- Easy Backup: A short backup key is all you need to safeguard your coin categories and labels, ensuring your organization remains intact.
Collaborative Multi-party Multisig
- Group Chat Integration: After creating your multisig wallet, Bitcoin Safe offers an encrypted nostr group chat for secure collaboration and one-click PSBT sharing.
- User Authentication: Each participant must authenticate every other user with a simple click, ensuring secure communication.
Watch and Learn: Get Started with Bitcoin Safe
If you’re new to Bitcoin Safe, a short video guide can make all the difference. Learn how to set up your Bitcoin Safe wallet in this detailed walk through:
https://youtu.be/m0g6ytYTy0w
Or see how to verify an address on your hardware singer:
https://youtu.be/h5FkOYj9OT8
Building up a knowledge base: https://bitcoin-safe.org/en/knowledge/
Whats next?
- Compact Block Filters!!! They make electrum servers obsolete.
- Why? Compact Block Filters increase the network privacy dramatically, since you're not asking an electrum server to give you your transactions
- Trade-off: They are a little slower than electrum servers. For a savings wallet like Bitcoin Safe this should be OK.
- How do they work? Simply speaking: They ask normal bitcoin core nodes for a short summary of each block. And if the summary shows a transaction belonging to the wallet, the entire block is then downloaded from the bitcoin core node. The bitcoin core node does not learn however which of the many transactions in the block you were interested in. Read more here and of course in the bip.
- When: 2 weeks 😅. Lots of things need to be done until Bitcoin Safe can use the bdk CBF/kyoto client from rustaceanrob, so keep an eye out for updates and please give feedback when you use Bitcoin Safe.
Stay updated on nostr or on GitHub.
Thank you
A huge thanks goes to nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f for supporting this project with a grant and nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx for the Hackathon prize.
This wallet is only possible because it is building upon other peoples open source work. Most notably
- bdk nostr:nprofile1qqsgkmgkmv63djkxmwvdlyaxx0xtsytvkyyg5fwzmp48pwd30f3jtxspzemhxue69uhhyetvv9ujuurjd9kkzmpwdejhgqg5waehxw309aex2mrp0yhxgctdw4eju6t0qyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqr8vuet
- and especially nostr:npub1thunderat5g552cuy7umk624ct5xe4tpgwr2jcjjq2gc0567wgrqnya79l , nostr:npub1reezn2ctrrg736uqj7mva9lsuwv0kr5asj4vvkwxnrwlhvxf98tsq99ty4 , and nostr:npub1ke470rdgnxg4gjs9cw3tv0dp690wl68f5xak5smflpsksedadd7qtf8jfm for dealing with my many feature requests and questions.
- rustaceanrob building kyoto which implements CBF for BDK; a crucial library and will be able to replace electrum servers for many use cases
- ndk by nostr:nprofile1qqsx3kq3vkgczq9hmfplc28h687py42yvms3zkyxh8nmkvn0vhkyyuspz4mhxue69uhkummnw3ezummcw3ezuer9wchsz9thwden5te0wfjkccte9ejxzmt4wvhxjme0qy88wumn8ghj7mn0wvhxcmmv9u0uehfp
And of course, secure storage of bitcoin is only possible, because of the hardware signer manufacturers. Thanks to nostr:npub1az9xj85cmxv8e9j9y80lvqp97crsqdu2fpu3srwthd99qfu9qsgstam8y8 Coldcard , Coldcard Q , nostr:npub1tg779rlap8t4qm8lpgn89k7mr7pkxpaulupp0nq5faywr8h28llsj3cxmt Bitbox02 , nostr:npub1jg552aulj07skd6e7y2hu0vl5g8nl5jvfw8jhn6jpjk0vjd0waksvl6n8n Blockstream Jade , Trezor Safe, Foundation Passport, Keystone, Ledger, Specter Shield, and many more.
I also want to thank people who gave feedback and helped spread the knowledge of Bitcoin Safe (please forgive me if I forgot to mention you)
- nostr:npub1p5cmlt32vc3jefkl3ymdvm9zk892fsmkq79eq77uvkaqrnyktasqkpkgaw nostr:npub1s07s0h5mwcenfnyagme8shp9trnv964lulgvdmppgenuhtk9p4rsueuk63 nostr:npub18f3g76xc7xs430euwwl9gpn7ue7ux8vmtm9q8htn9s26d8c4neeqdraz3s nostr:npub1mtd7s63xd85ykv09p7y8wvg754jpsfpplxknh5xr0pu938zf86fqygqxas nostr:npub1kysd8m44dhv7ywa75u5z7w2w0gs4t6qzhgvjp555gfknasy3krlqfxde60 nostr:npub185pu2dsgg9d36uvvw7rwuy9aknn8hnknygr7x2yqa60ygvq6r8kqc836k8 nostr:npub1hkcgyqnsuaradq3g5hyvfdekwypc25494nmwggwpygxas7fcs4fst860fu nostr:npub1xsl0msy347vmj8gcpsjum6wwppc4ercvq4xfrhqmek2dqmqm0mtsyf35vx nostr:npub1hxjnw53mhghumt590kgd3fmqme8jzwwflyxesmm50nnapmqdzu7swqagw3 nostr:npub1ke470rdgnxg4gjs9cw3tv0dp690wl68f5xak5smflpsksedadd7qtf8jfm nostr:npub1sk26fxl4fy3vt8m5n0a6aturaql0w20nvh22q0cyaqm28tj7z8ss3lutc9 nostr:npub1r4llq2jcvq4g2tgha5amjz07zk7mrrcj89wllny9xwhhp5zzkklqk4jwja nostr:npub1p9v2zpwl28c0gu0vr2enp3lwdtv29scwpeqsnt0ngqf03vtlyxfqhkae5w nostr:npub1xkym0yaewlz0qfghtt7hjtnu28fxaa5rk3wtcek9d3x3ft2ns3lq775few nostr:npub1r8343wqpra05l3jnc4jud4xz7vlnyeslf7gfsty7ahpf92rhfmpsmqwym8 nostr:npub12zpfs3yq7we83yvypgsrw5f88y2fv780c2kfs89ge5qk6q3sfm7spks880 nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx https://x.com/91xTx93x2 https://x.com/afilini rustaceanrob
-
 @ 06639a38:655f8f71
2025-03-17 15:13:22
@ 06639a38:655f8f71
2025-03-17 15:13:22- My PR#100 for
sirn-se/websocket-phpgot merged and was released in version 3.2.3 - Closed issue #83, reviewed and merged PR#84 for integrating NIP-04 and NIP-44
- Closed issue #85 and merged PR#86 with Event object verification
1.6.0release https://github.com/nostrver-se/nostr-php/releases/tag/1.6.0
Planned for week 12:
- Integrate NIP-19
- My PR#100 for
-
 @ dfbbf851:ba4542b5
2025-03-27 13:45:12
@ dfbbf851:ba4542b5
2025-03-27 13:45:12Bitcoin (BTC) เป็นสกุลเงินดิจิทัลที่ได้รับความนิยมและถูกพูดถึงมากที่สุดในโลก นับตั้งแต่เปิดตัวในปี 2009 โดยบุคคลหรือกลุ่มที่ใช้นามแฝงว่า Satoshi Nakamoto 🎭
แต่คำถามสำคัญก็คือ... Bitcoin เป็นอนาคตของการเงินโลกหรือว่าเป็นฟองสบู่ที่รอวันแตกกันแน่? 🤔
🔹 Bitcoin คืออะไร ?
Bitcoin เป็นเงินดิจิทัลที่ทำงานบน เทคโนโลยีบล็อกเชน (Blockchain) ซึ่งช่วยให้การทำธุรกรรมมีความปลอดภัยและโปร่งใส 💡
🔸 ไม่มีธนาคารกลางควบคุม 🔸 จำนวนจำกัดเพียง 21 ล้านเหรียญ 🔸 ใช้ระบบ "การขุด" (Mining) เพื่อยืนยันธุรกรรม
✅ ทำไม Bitcoin ได้รับความนิยม ?
✨ ไร้พรมแดน – โอนเงินข้ามประเทศได้รวดเร็วและถูกกว่าธนาคาร ✨ ความปลอดภัยสูง – ใช้ระบบเข้ารหัสที่แข็งแกร่ง 🔐 ✨ สินทรัพย์ป้องกันเงินเฟ้อ – มีจำนวนจำกัด จึงถูกมองว่าเป็น "ทองคำดิจิทัล" 🌎🏆 ✨ การยอมรับที่เพิ่มขึ้น – บริษัทใหญ่ เช่น Tesla และ PayPal เริ่มเปิดรับ BTC
❌ ความเสี่ยงของ Bitcoin
⚠️ ราคาผันผวนสูง – อาจขึ้นหรือลงหลายพันดอลลาร์ภายในวันเดียว 📉📈 ⚠️ ยังไม่ถูกยอมรับทั่วโลก – บางประเทศออกกฎหมายห้ามใช้ เช่น จีน 🚫 ⚠️ อาจถูกใช้ในทางผิดกฎหมาย – เช่น การฟอกเงินในตลาดมืด 🕵️♂️ ⚠️ สิ้นเปลืองพลังงาน – กระบวนการขุดใช้ไฟฟ้าปริมาณมาก ⚡🌱
🔮 อนาคตของ Bitcoin จะเป็นอย่างไร ?
นักลงทุนบางคนเชื่อว่า Bitcoin จะเป็นอนาคตของระบบการเงินโลก 💵🌍 ในขณะที่บางคนมองว่า มันเป็นเพียงฟองสบู่ที่อาจแตกเมื่อไหร่ก็ได้ 💥
💡 ปัจจัยสำคัญที่อาจกำหนดอนาคตของ BTC ได้แก่: ✔️ การยอมรับจากรัฐบาลและองค์กรใหญ่ ✔️ กฎหมายและกฎระเบียบ – หากรัฐบาลทั่วโลกออกกฎหมายสนับสนุน BTC อาจทำให้ราคาพุ่งสูง 🚀 ✔️ เทคโนโลยีใหม่ๆ – เช่น Lightning Network ที่ช่วยให้การทำธุรกรรมเร็วขึ้นและถูกลง ⚡
🎯 ปล.
Bitcoin เป็น นวัตกรรมการเงินที่เปลี่ยนโลก 🌎 และอาจกลายเป็นสินทรัพย์สำคัญในอนาคต แต่ก็มีความเสี่ยงสูง นักลงทุนต้องศึกษาให้รอบคอบก่อนตัดสินใจลงทุน 📊💡
แล้วท่านผู้อ่านล่ะครับ คิดว่า Bitcoin คืออนาคตของเงิน หรือเป็นเพียงกระแสชั่วคราวกันแน่ ? 🤔
Bitcoin #Crypto #Blockchain #BTC #ลงทุน #การเงิน #อนาคตการเงิน
-
 @ 06639a38:655f8f71
2025-03-17 14:55:18
@ 06639a38:655f8f71
2025-03-17 14:55:18https://ccns.nostrver.se is a (Drupal powered) website that I started to build in January 2024 (source on Github and Gitlab). It's a fork of an earlier (abandoned) project https://cchs.social/.
Currently CCNS is a link aggregration website and for now it's only my who is using it to save and share Nostr related links. When you post a new link, you have the option to cross-post it as a Nostr note (example here).Kind 39700
Last month Jurjen and Abir has started to work on a social bookmark client built with Nostr (inspired by Del.icio.us from the past). Earlier this month they changed to event kind 39700 for broadcasting the Nostr event with the bookmark / link data accross the network. They did this because Sep already created a social bookmark like client called Pinja when fiatjaf raised this idea.
With these developments to me it was very obvious to integrate the feature that new created CCNS links are now also published as kind 39700 events to the Nostr network. This means that links are now also distributed on multiple relays as kind 39700 events and are accessible in multiple clients (Yumyume and Pinja).
Here you can see the same data, from left to right:

Structure
The current data structure for the 39700 kind looks as follow:
- "id": "event_id"
- "pubkey": "pubkey author"
- "created_at": unix_timestamp
- "kind": 39700
- "tags":
- "description", "description text here"
- "d", "unique-slug-value"
- "t", "hashtag"
- "content": "https://book_mark_url"
- "sig": "signature"
As there is no NIP (yet) for this event kind, I see some possible improvements:
- Use the bookmark URL as
dtag so it can be used as a unique identifier for every client - Use the content field for the description
- Use the
atag for an addressable event following NIP-01:["a", "39700:pubkey_of_author:", recommended_relay_url_optional]
On short-term I don't have any plans to developer CCNS further, as most of my attention goes to the development of the Nostr-PHP library and Drupal related contribs using that library. That said, CCNS is a Drupal project but all the Nostr stuff is done client-side (Javascript) with NDK and Nostr-PHP is not used (maybe this will change in the future).
-
 @ dfbbf851:ba4542b5
2025-03-27 13:43:45
@ dfbbf851:ba4542b5
2025-03-27 13:43:45🌟 บทนำ
ในยุคดิจิทัลที่ทุกอย่างขับเคลื่อนด้วยเทคโนโลยี Blockchain เป็นหนึ่งในนวัตกรรมที่สร้างแรงสั่นสะเทือนมากที่สุด 🌍 หลายคนอาจรู้จัก Blockchain ผ่าน Bitcoin หรือ Ethereum แต่จริงๆ แล้ว มันสามารถนำไปใช้ได้หลากหลายกว่าที่คุณคิด !
💡 ลองจินตนาการถึงโลกที่ไม่มีตัวกลาง ไม่มีการโกงข้อมูล และทุกธุรกรรมสามารถตรวจสอบได้แบบ 100%... นี่แหละคือ พลังของ Blockchain !
🔎 Blockchain คืออะไร ?
Blockchain เป็นเทคโนโลยีที่ทำให้ข้อมูลมีความ ปลอดภัย โปร่งใส และแก้ไขไม่ได้ ✅ ทุกธุรกรรมที่เกิดขึ้นจะถูกบันทึกลงใน "บล็อก" และเชื่อมต่อกันเป็นโซ่ (Chain) ซึ่งทำให้:
✅ ไม่มีตัวกลาง (Decentralization) – ไม่ต้องพึ่งธนาคารหรือบริษัทใดๆ ✅ ปลอมแปลงยาก (Security) – ใช้การเข้ารหัสระดับสูง 🔐 ✅ โปร่งใสตรวจสอบได้ (Transparency) – ทุกคนสามารถเข้าดูข้อมูลได้แบบเรียลไทม์
⚙️ Blockchain ทำงานอย่างไร ?
1️⃣ ธุรกรรมถูกสร้างขึ้น เช่น การโอนเงิน 💸 2️⃣ เครือข่ายตรวจสอบความถูกต้อง ผ่านกลไกอย่าง Proof of Work (PoW) หรือ Proof of Stake (PoS) 3️⃣ ธุรกรรมถูกบันทึกลงบล็อก และเชื่อมโยงกับบล็อกก่อนหน้า 🔗 4️⃣ ข้อมูลถูกกระจายไปยังทุกโหนด ทำให้ไม่สามารถถูกแก้ไขย้อนหลังได้
✨ ง่ายๆ คือ Blockchain ทำให้ข้อมูลมีความน่าเชื่อถือ และไม่มีใครสามารถควบคุมได้เพียงลำพัง !
💡 การประยุกต์ใช้ Blockchain ในโลกธุรกิจ
🔥 การเงินและธนาคาร – ลดค่าธรรมเนียมการโอนเงินระหว่างประเทศ 🏦 🔥 Supply Chain – ติดตามสินค้าแบบเรียลไทม์ ป้องกันของปลอม 📦 🔥 การดูแลสุขภาพ – จัดเก็บข้อมูลผู้ป่วยแบบปลอดภัย 🏥 🔥 อสังหาริมทรัพย์ – ซื้อขายบ้านโดยไม่ต้องพึ่งนายหน้า 🏡 🔥 การเลือกตั้ง – ป้องกันการโกงเสียงเลือกตั้งผ่านระบบดิจิทัล 🗳️
🚀 อนาคตของ Blockchain
Blockchain กำลังพัฒนาไปสู่เทคโนโลยีที่มีความ เร็วขึ้น ปลอดภัยขึ้น และใช้พลังงานน้อยลง ♻️ เทรนด์ที่น่าจับตามอง ได้แก่:
🔹 CBDC (เงินดิจิทัลของธนาคารกลาง) – กำลังมาแรง! 🔹 DeFi (การเงินแบบไร้ตัวกลาง) – พลิกโฉมการลงทุน 🔹 NFT (สินทรัพย์ดิจิทัลไม่ซ้ำกัน) – ปฏิวัติวงการศิลปะ 🎨
แม้ว่าจะยังมีข้อท้าทาย เช่น ค่าธรรมเนียมสูง หรือการใช้พลังงานมากในบางระบบ แต่ Blockchain กำลังมุ่งสู่อนาคตที่ยั่งยืนและเป็นมิตรกับสิ่งแวดล้อมมากขึ้น 🌱
🎯 ปล.
Blockchain ไม่ใช่แค่เรื่องของ Bitcoin ! แต่เป็นเทคโนโลยีที่สามารถเปลี่ยนโลกในหลายด้าน 🌎 หากคุณเป็นนักธุรกิจ นักลงทุน หรือเพียงแค่คนที่อยากเข้าใจโลกดิจิทัลมากขึ้น นี่คือเทคโนโลยีที่คุณไม่ควรมองข้าม !
📢 แล้วคุณล่ะ คิดว่า Blockchain จะเปลี่ยนโลกไปอย่างไรบ้าง? มาพูดคุยกันในคอมเมนต์ได้เลย! 👇💬
Blockchain #Crypto #DeFi #NFT #Web3 #Bitcoin #Innovation
-
 @ b5d34eed:a7475cbf
2025-03-16 20:15:10
@ b5d34eed:a7475cbf
2025-03-16 20:15:10The internet has come a long way since its inception, but let’s be honest—it’s not exactly the utopia of freedom and openness we once imagined. Today, a handful of tech giants control most of our online interactions, from social media to payments. Enter the decentralized web, a movement that’s pushing back against this centralization. At the forefront of this revolution is Nostr, a simple yet powerful protocol that’s redefining how we think about social networking. And when you throw the Lightning Network into the mix, things get even more exciting. Let’s break it all down.
What’s Wrong with the Current Web?
Before we dive into Nostr, let’s talk about why decentralization matters. The internet today is dominated by centralized platforms like Facebook, Twitter (now X), and Instagram. These platforms control what you see, how you interact, and even what you’re allowed to say. They harvest your data, sell it to advertisers, and can ban or silence you at their discretion. It’s a system that prioritizes profit over people.
Centralization also creates single points of failure. If a platform goes down, gets hacked, or decides to shut down, your data and connections disappear overnight. Remember when Twitter had outages, or when Facebook’s servers crashed? Millions of users were left stranded. This isn’t just inconvenient—it’s a fundamental flaw in how we’ve built the web.
Enter Nostr: A Breath of Fresh Air
Nostr, which stands for Notes and Other Stuff Transmitted by Relays, is a decentralized protocol designed to fix these problems. Unlike traditional social media platforms, Nostr doesn’t rely on a central server. Instead, it uses a network of independent relays to transmit messages. Think of it as a decentralized Twitter, but without the corporate overlords.
Here’s why Nostr is a game-changer:
-
No Central Authority: Nostr doesn’t belong to any company or individual. It’s an open protocol, meaning anyone can build apps on top of it or run their own relay. This eliminates the risk of censorship or arbitrary bans.
-
User Control: With Nostr, you own your data. Your posts, messages, and connections are stored locally or on relays you choose. If one relay goes down, you can switch to another without losing anything.
-
Interoperability: Nostr is designed to work across different apps and platforms. This means you’re not locked into a single ecosystem. If you don’t like one Nostr client, you can switch to another without losing your followers or content.
-
Simplicity: Nostr’s protocol is intentionally simple. It doesn’t try to do everything at once, which makes it lightweight and easy to use. This simplicity also makes it more resilient and adaptable.
The Lightning Network: Powering Decentralized Payments
Now, let’s talk about money. One of the coolest things about Nostr is its integration with the Lightning Network, a second-layer payment protocol built on top of Bitcoin. The Lightning Network enables fast, cheap, and scalable transactions, making it perfect for micropayments and tipping.
Here’s why this matters:
-
Monetization Without Ads: Traditional social media platforms rely on ads to make money. This creates a perverse incentive to keep you hooked and harvest your data. With Nostr and the Lightning Network, creators can monetize their content directly through tips or paid subscriptions. No ads, no middlemen—just a direct connection between creators and their audience.
-
Global Payments: The Lightning Network is borderless. Whether you’re tipping a blogger in Nigeria or buying a digital product from someone in Argentina, transactions are instant and cost just a fraction of a cent. This opens up new opportunities for global collaboration and commerce.
-
Censorship-Resistant Money: Just like Nostr resists censorship, the Lightning Network ensures that payments can’t be blocked or controlled by any central authority. This is especially important in regions where financial freedom is under threat.
Why Nostr and the Lightning Network Are a Perfect Match
When you combine Nostr’s decentralized social networking with the Lightning Network’s payment capabilities, you get something truly special. Imagine a social media platform where you can tip your favorite creators, pay for premium content, or even buy goods and services—all without leaving the app. And because both Nostr and the Lightning Network are decentralized, you don’t have to worry about fees, censorship, or corporate interference.
For example, let’s say you’re a musician sharing your work on Nostr. Fans can tip you in Bitcoin via the Lightning Network, or you can sell exclusive content directly to your followers. The money goes straight to you, without a platform taking a cut. This creates a more equitable and sustainable model for creators.
The Bigger Picture: A Decentralized Future
Nostr and the Lightning Network are just two pieces of a much larger puzzle. The decentralized web is about reclaiming control over our online lives—our data, our interactions, and our money. It’s about building a more open, resilient, and user-centric internet.
Of course, decentralization isn’t without its challenges. It can be harder to use than centralized alternatives, and it requires a shift in how we think about technology. But the benefits far outweigh the drawbacks. By embracing protocols like Nostr and the Lightning Network, we can create a web that’s truly by the people, for the people.
Final Thoughts
The decentralized web isn’t just a tech trend—it’s a movement. Nostr and the Lightning Network are proof that we can build better, fairer systems when we prioritize freedom and innovation over profit and control. Whether you’re a creator, a developer, or just someone who’s tired of Big Tech’s grip on your online life, now’s the time to explore what the decentralized web has to offer.
-
-
 @ 7d33ba57:1b82db35
2025-03-27 10:53:58
@ 7d33ba57:1b82db35
2025-03-27 10:53:58Sitges is known for its golden beaches, vibrant nightlife, and artistic charm. With a beautiful seafront promenade, historic old town, and a welcoming atmosphere, it’s a top destination for relaxation, culture, and fun on the **Costa Dorada.
🏖️ Top Things to See & Do in Sitges
1️⃣ Stroll Along the Passeig Marítim 🌊
- A scenic seaside promenade lined with palm trees, beaches, and restaurants.
- Perfect for walking, cycling, or enjoying a sunset cocktail.
2️⃣ Relax on the Beaches 🏖️
- Playa de la Fragata – A central beach near the old town, great for families.
- Playa de San Sebastián – A smaller, quieter beach with local charm.
- Playa del Balmins – A well-known nudist and LGBTQ+ friendly beach.
- Playa de l'Home Mort – A hidden cove, popular for naturists.

3️⃣ Visit the Church of Sant Bartomeu i Santa Tecla ⛪
- The iconic church overlooking the sea, a must-visit landmark.
- Amazing spot for photos, especially at sunset.
4️⃣ Explore the Old Town & Museums 🏛️
- Wander through charming whitewashed streets filled with boutique shops and cafés.
- Visit Museu Cau Ferrat, home to art by Santiago Rusiñol and Picasso.
- Discover Museu Maricel, featuring Romanesque and modernist art.
5️⃣ Enjoy Sitges' Lively Nightlife & Festivals 🎭
- Sitges is famous for its bars, beach clubs, and LGBTQ+ friendly nightlife.
- Visit in February for Sitges Carnival, one of Spain’s best! 🎉
- Experience the Sitges Film Festival (October), known for horror & fantasy films.
6️⃣ Wine Tasting in Penedès 🍷
- Take a short trip to Penedès, one of Spain’s best Cava (sparkling wine) regions.
- Tour local wineries and enjoy wine tastings just 30 minutes away.
🍽️ What to Eat in Sitges
- Xató – A local salad with cod, anchovies, and romesco sauce 🥗
- Suquet de Peix – A Catalan seafood stew with potatoes 🍲🐟
- Fideuà – Similar to paella, but made with short noodles instead of rice 🍤
- Crema Catalana – A delicious caramelized custard dessert 🍮
- Cava – The famous Catalan sparkling wine from nearby Penedès 🍾
🚗 How to Get to Sitges
🚆 By Train: 35 min from Barcelona (Sants or Passeig de Gràcia stations).
🚘 By Car: 40 min from Barcelona via the C-32 highway.
🚌 By Bus: Direct buses from Barcelona Airport (El Prat) and Tarragona.
✈️ By Air: The nearest airport is Barcelona-El Prat (BCN, 25 km away).💡 Tips for Visiting Sitges
✅ Best time to visit? Spring to early autumn (April–October) for beach weather ☀️
✅ Avoid summer weekends – It gets very busy with visitors from Barcelona 🏖️
✅ Visit during Carnival or the Film Festival for an unforgettable experience 🎭🎬
✅ Explore beyond the beaches – The old town and vineyards are worth it! 🍷
✅ Try beachfront dining – Enjoy fresh seafood with a sea view 🍽️🌊 -
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 57d1a264:69f1fee1
2025-03-27 10:42:05
@ 57d1a264:69f1fee1
2025-03-27 10:42:05What we have been missing in SN Press kit? Most important, who the press kit is for? It's for us? It's for them? Them, who?
The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we speek out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1:
Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.
Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before.
This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using.
@k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful.
[^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined
originally posted at https://stacker.news/items/926557
-
 @ a95c6243:d345522c
2025-03-15 10:56:08
@ a95c6243:d345522c
2025-03-15 10:56:08Was nützt die schönste Schuldenbremse, wenn der Russe vor der Tür steht? \ Wir können uns verteidigen lernen oder alle Russisch lernen. \ Jens Spahn
In der Politik ist buchstäblich keine Idee zu riskant, kein Mittel zu schäbig und keine Lüge zu dreist, als dass sie nicht benutzt würden. Aber der Clou ist, dass diese Masche immer noch funktioniert, wenn nicht sogar immer besser. Ist das alles wirklich so schwer zu durchschauen? Mir fehlen langsam die Worte.
Aktuell werden sowohl in der Europäischen Union als auch in Deutschland riesige Milliardenpakete für die Aufrüstung – also für die Rüstungsindustrie – geschnürt. Die EU will 800 Milliarden Euro locker machen, in Deutschland sollen es 500 Milliarden «Sondervermögen» sein. Verteidigung nennen das unsere «Führer», innerhalb der Union und auch an «unserer Ostflanke», der Ukraine.
Das nötige Feindbild konnte inzwischen signifikant erweitert werden. Schuld an allem und zudem gefährlich ist nicht mehr nur Putin, sondern jetzt auch Trump. Europa müsse sich sowohl gegen Russland als auch gegen die USA schützen und rüsten, wird uns eingetrichtert.
Und während durch Diplomatie genau dieser beiden Staaten gerade endlich mal Bewegung in die Bemühungen um einen Frieden oder wenigstens einen Waffenstillstand in der Ukraine kommt, rasselt man im moralisch überlegenen Zeigefinger-Europa so richtig mit dem Säbel.
Begleitet und gestützt wird der ganze Prozess – wie sollte es anders sein – von den «Qualitätsmedien». Dass Russland einen Angriff auf «Europa» plant, weiß nicht nur der deutsche Verteidigungsminister (und mit Abstand beliebteste Politiker) Pistorius, sondern dank ihnen auch jedes Kind. Uns bleiben nur noch wenige Jahre. Zum Glück bereitet sich die Bundeswehr schon sehr konkret auf einen Krieg vor.
Die FAZ und Corona-Gesundheitsminister Spahn markieren einen traurigen Höhepunkt. Hier haben sich «politische und publizistische Verantwortungslosigkeit propagandistisch gegenseitig befruchtet», wie es bei den NachDenkSeiten heißt. Die Aussage Spahns in dem Interview, «der Russe steht vor der Tür», ist das eine. Die Zeitung verschärfte die Sache jedoch, indem sie das Zitat explizit in den Titel übernahm, der in einer ersten Version scheinbar zu harmlos war.
Eine große Mehrheit der deutschen Bevölkerung findet Aufrüstung und mehr Schulden toll, wie ARD und ZDF sehr passend ermittelt haben wollen. Ähnliches gelte für eine noch stärkere militärische Unterstützung der Ukraine. Etwas skeptischer seien die Befragten bezüglich der Entsendung von Bundeswehrsoldaten dorthin, aber immerhin etwa fifty-fifty.
Eigentlich ist jedoch die Meinung der Menschen in «unseren Demokratien» irrelevant. Sowohl in der Europäischen Union als auch in Deutschland sind die «Eliten» offenbar der Ansicht, der Souverän habe in Fragen von Krieg und Frieden sowie von aberwitzigen astronomischen Schulden kein Wörtchen mitzureden. Frau von der Leyen möchte über 150 Milliarden aus dem Gesamtpaket unter Verwendung von Artikel 122 des EU-Vertrags ohne das Europäische Parlament entscheiden – wenn auch nicht völlig kritiklos.
In Deutschland wollen CDU/CSU und SPD zur Aufweichung der «Schuldenbremse» mehrere Änderungen des Grundgesetzes durch das abgewählte Parlament peitschen. Dieser Versuch, mit dem alten Bundestag eine Zweidrittelmehrheit zu erzielen, die im neuen nicht mehr gegeben wäre, ist mindestens verfassungsrechtlich umstritten.
Das Manöver scheint aber zu funktionieren. Heute haben die Grünen zugestimmt, nachdem Kanzlerkandidat Merz läppische 100 Milliarden für «irgendwas mit Klima» zugesichert hatte. Die Abstimmung im Plenum soll am kommenden Dienstag erfolgen – nur eine Woche, bevor sich der neu gewählte Bundestag konstituieren wird.
Interessant sind die Argumente, die BlackRocker Merz für seine Attacke auf Grundgesetz und Demokratie ins Feld führt. Abgesehen von der angeblichen Eile, «unsere Verteidigungsfähigkeit deutlich zu erhöhen» (ausgelöst unter anderem durch «die Münchner Sicherheitskonferenz und die Ereignisse im Weißen Haus»), ließ uns der CDU-Chef wissen, dass Deutschland einfach auf die internationale Bühne zurück müsse. Merz schwadronierte gefährlich mehrdeutig:
«Die ganze Welt schaut in diesen Tagen und Wochen auf Deutschland. Wir haben in der Europäischen Union und auf der Welt eine Aufgabe, die weit über die Grenzen unseres eigenen Landes hinausgeht.»
[Titelbild: Tag des Sieges]
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 7d33ba57:1b82db35
2025-03-27 10:35:25
@ 7d33ba57:1b82db35
2025-03-27 10:35:25Nerja is known for its stunning beaches, famous caves, and breathtaking sea views. With a charming old town, whitewashed houses, and a lively atmosphere, Nerja offers a perfect mix of relaxation, nature, and culture.
🏖️ Top Things to See & Do in Nerja
1️⃣ Balcón de Europa 🌅
- A stunning viewpoint with panoramic views of the Mediterranean.
- Lined with palm trees, street musicians, and cafés.
- A great spot for sunset photos and people-watching.
2️⃣ Nerja Caves (Cuevas de Nerja) 🏰
- A famous cave system with impressive stalactites and stalagmites.
- Home to prehistoric cave paintings, estimated to be over 40,000 years old.
- One of Spain’s most important archaeological sites.
3️⃣ Playa de Burriana 🏖️
- The best beach in Nerja, with golden sand and clear waters.
- Offers water sports, including kayaking and paddleboarding.
- Many chiringuitos (beach bars) serving delicious seafood paella.
4️⃣ Kayaking to Maro Cliffs 🚣♂️
- Paddle along the coastline to discover hidden coves and waterfalls.
- A unique way to explore the Maro-Cerro Gordo Cliffs Natural Park.
5️⃣ Frigiliana – The Most Beautiful White Village 🏡
- Just 10 minutes from Nerja, this charming Andalusian village is full of whitewashed houses, cobbled streets, and colorful flowers.
- Wander through narrow alleyways and enjoy stunning mountain views.
6️⃣ El Salón & Calahonda Beaches 🏝️
- Small, quiet beaches just below the Balcón de Europa.
- Perfect for a relaxing swim away from the crowds.
🍽️ What to Eat in Nerja
- Espetos de Sardinas – Grilled sardines on skewers, a classic Andalusian dish 🐟
- Ajoblanco – A cold almond and garlic soup, refreshing on hot days 🍲
- Fried Fish (Pescaito Frito) – A mix of freshly caught seafood 🦑🐠
- Tarta de Almendra – A traditional almond cake, perfect with coffee 🍰
- Paella at Playa Burriana – One of the best places to enjoy authentic seafood paella 🍤🍚
🚗 How to Get to Nerja
✈️ By Air: The nearest airport is Málaga Airport (AGP, 70 km, 50 min drive).
🚘 By Car: 50 min from Málaga, 1.5 hrs from Granada.
🚌 By Bus: Direct buses from Málaga, Granada, and other Costa del Sol towns.
🚆 By Train: No direct train, but you can take a train to Málaga and then a bus.💡 Tips for Visiting Nerja
✅ Best time to visit? Spring & summer (April–September) for the best weather ☀️
✅ Book Nerja Cave tickets in advance – It’s one of the most visited sites in Andalusia 🏰
✅ Try kayaking or boat tours – The coastline is stunning from the water 🚣♂️
✅ Visit Frigiliana early – To avoid crowds and enjoy the peaceful morning atmosphere 🌅
✅ Wear comfortable shoes – The old town has steep, cobbled streets 👟
-
 @ 3197ad60:7a122b95
2025-03-14 20:00:01
@ 3197ad60:7a122b95
2025-03-14 20:00:01I’m working on my portfolio. I will take it with me to the Children’s Book Fair in Bologna, to stand in very long queues, hoping to show it to some people in the publishing industry.
Preparing a portfolio could be a moment of celebration of all the work I have done and want to share with the world. Wouldn’t that be wonderful?
Instead, it slowly and quietly became a litany of the “could”s and “should”s and “must ”s: I could include all the work that’s even remotely relevant, I should probably showcase a range of skills, and therefore I must create a bunch of completely new work to appeal to every possible audience.
Maybe I need a range of deep, magical forest backgrounds, or a unicorn flying over a London night sky, or a coral reef with jellyfish playing poker, painted in very bright colours. Just to show that I can.

Well, that quickly became a downward spiral of stress-induced ideas for illustrations I don’t have time to make. Even though I enjoyed the work I was doing, in that mindset, no matter what I do, it’s never enough.
And then, lo and behold, I looked through my sketchbook. I was looking for something specific, a texture or a colour from a sketch that I’ve done. I opened one sketchbook looking for it, then another one, then one more.
There was so much work looking back at me wherever I turned. After all, I’ve been drawing daily since last July, sometimes from life, sometimes from imagination. Inevitably, I created a lot of work: paintings, drawings, sketches, and finished illustrations. Only looking through my work did I realise that I will always feel the push to make more work for my portfolio; because my style keeps evolving, I’m able to draw more and better with every step. But is the work I’ve done so far, enough to show where I am as an illustrator? Hell yeah.
Many cliches come to mind (because they’re true!) but my favourite is: don’t compare yourself to others, only compare to yourself from the past.
This is the third year of me going to Bologna for the fair, and the first time I will bring a portfolio with me. That means whatever I do is already 100% more than what I’ve done before. That’s a much better way to think about it.
Chill, Martyna, you’ve got this.
Thanks for reading.
x

-
 @ da0b9bc3:4e30a4a9
2025-03-27 10:21:42
@ da0b9bc3:4e30a4a9
2025-03-27 10:21:42Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/926553
-
 @ 6ad08392:ea301584
2025-03-14 19:03:20
@ 6ad08392:ea301584
2025-03-14 19:03:20In 2024, I was high as a kite on Nostr hopium and optimism. Early that year, my co-founder and I figured that we could use Nostr as a way to validate ambassadors on “Destination Bitcoin” - the germ of a travel app idea we had at the time that would turn into Satlantis. After some more digging and thinking, we realised that Nostr’s open social graph would be of major benefit, and in exploring that design space, the fuller idea of Satlantis formed: a new kind of social network for travel.
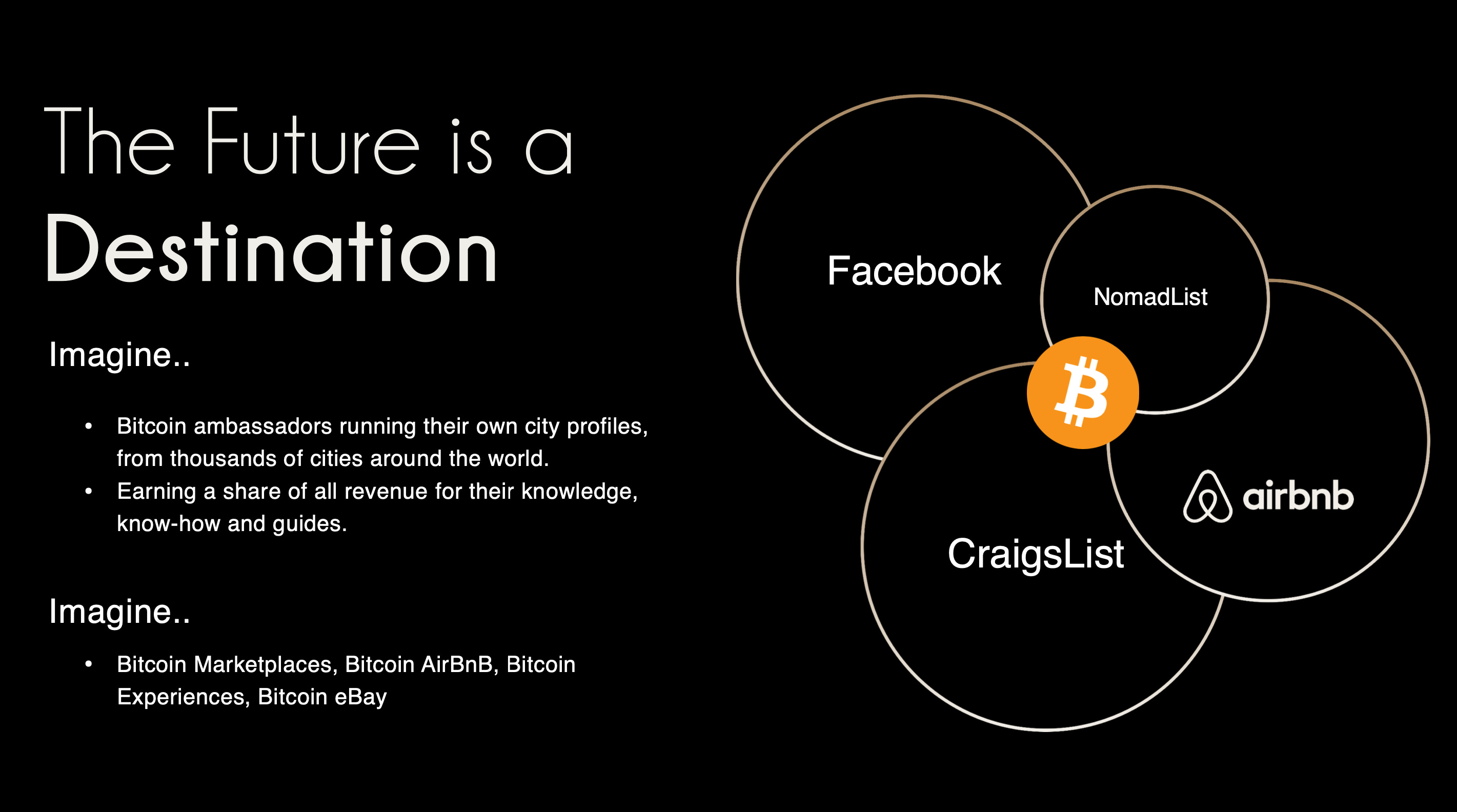 ###### ^^2 slides from the original idea here
###### ^^2 slides from the original idea hereI still remember the call I had with @pablof7z in January. I was in Dubai pitching the AI idea I was working on at the time, but all I could think and talk about was Satlantis and Nostr.
That conversation made me bullish AF. I came back from the trip convinced we’d struck gold. I pivoted the old company, re-organised the team and booked us for the Sovereign Engineering cohort in Madeira. We put together a whole product roadmap, go to market strategy and cap raise around the use of Nostr. We were going to be the ‘next big Nostr app’.
A couple of events followed in which I announced this all to the world: Bitcoin Atlantis in March and BTC Prague in June being the two main ones. The feedback was incredible. So we doubled down. After being the major financial backer for the Nostr Booth in Prague, I decided to help organise the Nostr Booth initiative and back it financially for a series of Latin American conferences in November. I was convinced this was the biggest thing since bitcoin, so much so that I spent over $50,000 in 2024 on Nostr marketing initiatives. I was certainly high on something.
Sobering up
It’s March 2025 and I’ve sobered up. I now look at Nostr through a different lens. A more pragmatic one. I see Nostr as a tool, as an entrepreneur - who’s more interested in solving a problem, than fixating on the tool(s) being used - should.
A couple things changed for me. One was the sub-standard product we released in November. I was so focused on being a Nostr evangelist that I put our product second. Coupled with the extra technical debt we took on at Satlantis by making everything Nostr native, our product was crap. We traded usability & product stability for Nostr purism & evangelism.
We built a whole suite of features using native event kinds (location kinds, calendar kinds, etc) that we thought other Nostr apps would also use and therefore be interoperable. Turns out no serious players were doing any of that, so we spent a bunch of time over-engineering for no benefit 😂
The other wake up call for me was the Twitter ban in Brazil. Being one of the largest markets for Twitter, I really thought it would have a material impact on global Nostr adoption. When basically nothing happened, I began to question things.
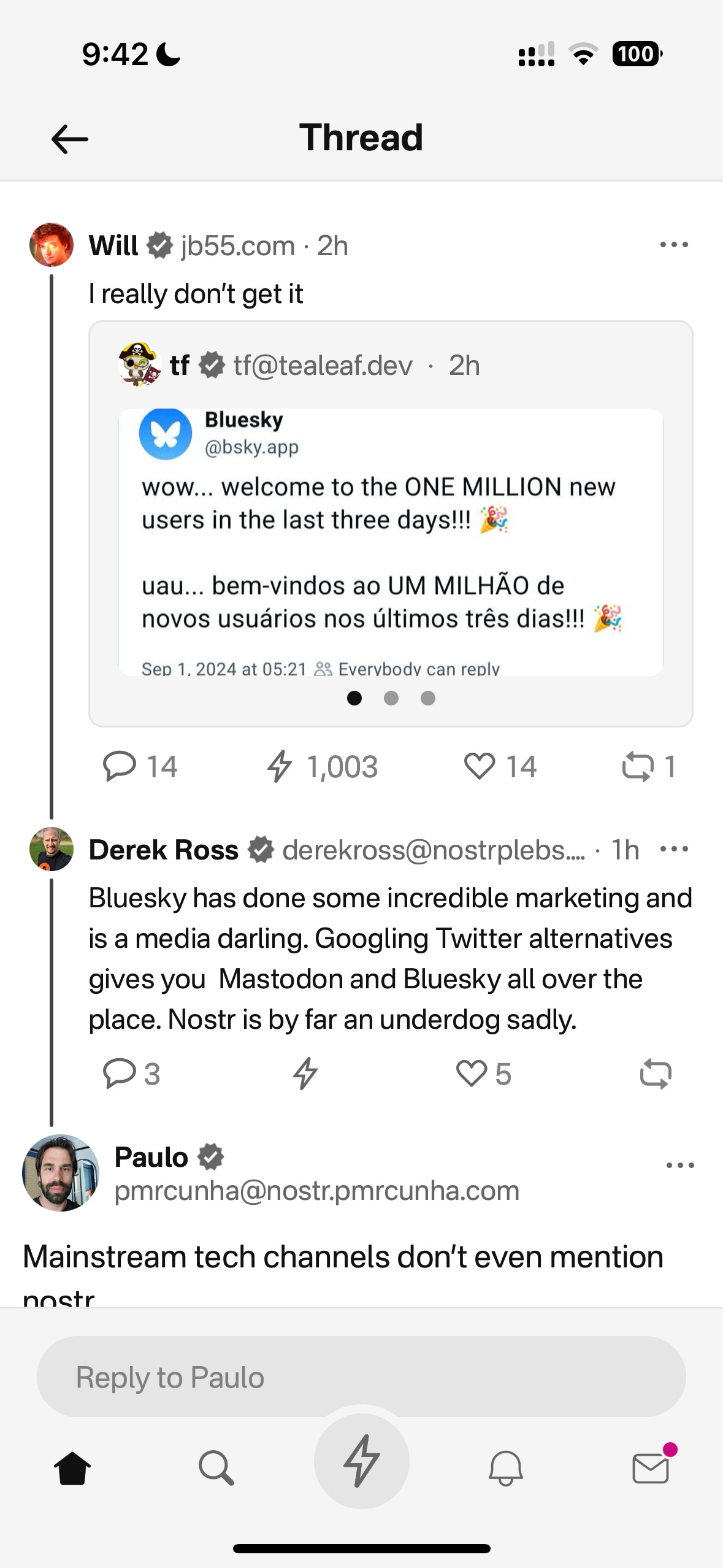
Combined, these experiences helped sober me up and I come down from my high. I was reading “the cold start problem” by Andrew Chen (ex-Uber) at the time and doing a deep dive on network effects. I came to the following realisation:
Nostr’s network effect is going to take WAY longer than we all anticipated initially. This is going to be a long grind. And unlike bitcoin, winning is not inevitable. Bitcoin solves a much more important problem, and it’s the ONLY option. Nostr solves an important problem yes, but it’s far from the only approach. It’s just the implementation arguably in the lead right now.
This sobering up led us to take a different approach with Nostr. We now view it as another tool in the tech-stack, no different to the use of React Native on mobile or AWS for infrastructure. Nostr is something to use if it makes the product better, or avoid if it makes the product and user experience worse. I will share more on this below, including our simple decision making framework. I’ll also present a few more potentially unpopular opinions about Nostr. Four in total actually:
- Nostr is a tool, not a revolution
- Nostr doesn’t solve the multiple social accounts problem
- Nostr is not for censorship resistance
- Grants come with a price
Let’s begin…
Nostr is a tool, not a revolution
Nostr is full of Bitcoiners, and as much as we like to think we’re immune from shiny object syndrome, we are, somewhere deep down afflicted by it like other humans. That’s normal & fine. But…while Bitcoiners have successfully suppressed this desire when it comes to shitcoins, it lies dormant, yearning for the least shitcoin-like thing to emerge which we can throw our guiltless support behind.
That thing arrived and it’s called Nostr.
As a result, we’ve come to project the same kind of purity and maximalism onto it as we do with Bitcoin, because it shares some attributes and it’s clearly not a grift.
The trouble is, in doing so, we’ve put it in the same class as Bitcoin - which is an error.
Nostr is important and in its own small way, revolutionary, but it pales in comparison to Bitcoin’s importance. Think of it this way: If Bitcoin fails, civilisation is fucked. If Nostr fails, we’ll engineer another rich-identity protocol. There is no need for the kind of immaculate conception and path dependence that was necessary for Bitcoin whose genesis and success has been a once in a civilisation event. Equivocating Nostr and Bitcoin to the degree that it has been, is a significant category error. Nostr may ‘win’ or it may just be an experiment on the path to something better. And that’s ok !
I don’t say this to piss anyone off, to piss on Nostr or to piss on myself. I say it because I’d prefer Nostr not remain a place where a few thousand people speak to each other about how cool Nostr is. That’s cute in the short term, but in the grand scheme of things, it’s a waste of a great tool that can make a significant corner of the Internet great again.
By removing the emotional charge and hopium from our relationship to Nostr, we can take a more sober, objective view of it (and hopefully use it more effectively).
Instead of making everything about Nostr (the tool), we can go back to doing what great product people and businesses do: make everything about the customer.
Nobody’s going around marketing their app as a “react native product” - and while I understand that’s a false equivalent in the sense that Nostr is a protocol, while react is a framework - the reality is that it DOES NOT MATTER.
For 99.9999% of the world, what matters is the hole, not the drill. Maybe 1000 people on Earth REALLY care that something is built on Nostr, but for everyone else, what matters is what the app or product does and the problem it solves. Realigning our focus in this way, and looking at not only Nostr, but also Bitcoin as a tool in the toolkit, has transformed the way we’re building.
This inspired an essay I wrote a couple weeks ago called “As Nostr as Possible”. It covers our updated approach to using and building WITH Nostr (not just ‘on’ it). You can find that here:
https://futuresocial.substack.com/p/as-nostr-as-possible-anap
If you’re too busy to read it, don’t fret. The entire theory can be summarised by the diagram below. This is how we now decide what to make Nostr-native, and what to just build on our own. And - as stated in the ANAP essay - that doesn’t mean we’ll never make certain features Nostr-native. If the argument is that Nostr is not going anywhere, then we can always come back to that feature and Nostr-fy it later when resources and protocol stability permit.
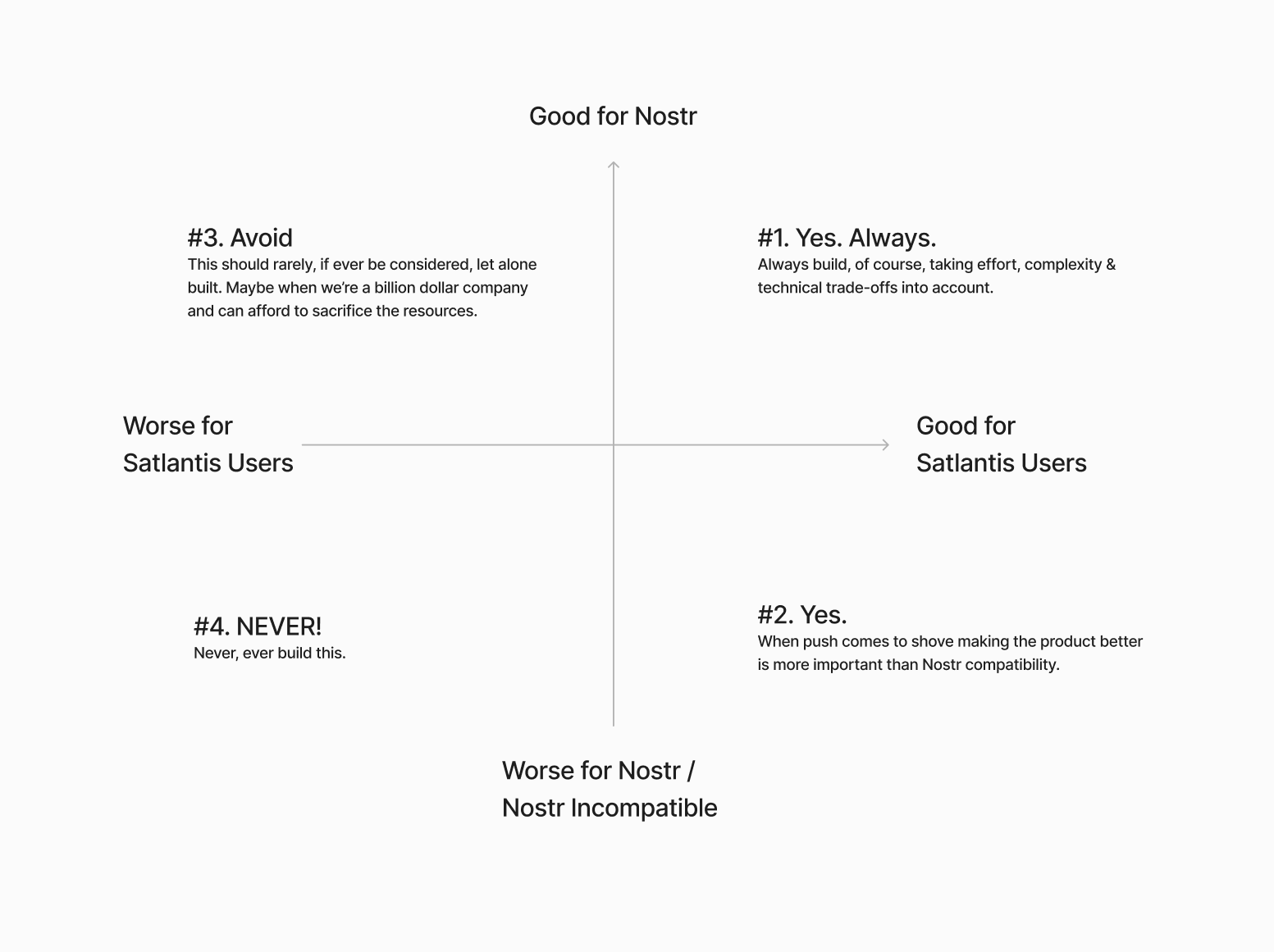
Next…
The Nostr all in one approach is not all “positive”
Having one account accessible via many different apps might not be as positive as we initially thought.

If you have one unified presence online, across all of your socials, and you’re posting the same thing everywhere, then yes - being able to post content in one place and it being broadcast everywhere, is great. There’s a reason why people literally PAY for products like Hypefury, Buffer and Hootsuite (aside from scheduling).
BUT…..This is not always the case.
I’ve spoken to hundreds of creators and many have flagged this as a bug not a feature because they tend to have a different audience on different platforms and speak to them differently depending on the platform. We all know this. How you present yourself on LinkedIn is very different to how you do it on Instagram or X.
The story of Weishu (Tencent’s version of TikTok) comes to mind here. Tencent’s WeChat login worked against them because people didn’t want their social graph following them around. Users actually wanted freedom from their existing family & friends, so they chose Douyin (Chinese TikTok) instead.
Perhaps this is more relevant to something like WeChat because the social graph following you around is more personal, but we saw something similar with Instagram and Facebook. Despite over a decade of ownership, Facebook still keeps the social graphs separated.
All this to say that while having a different strategy & approach on different social apps is annoying, it allows users to tap into different markets because each silo has its own ‘flavour’. The people who just post the same thing everywhere are low-quality content creators anyway. The ones who actually care, are using each platform differently.
The ironic part here is that this is arguably more ‘decentralised’ than the protocol approach because these siloes form a ‘marketplace of communities’ which are all somewhat different.
We need to find a smart way of doing this with Nostr. Some way of catering to the appropriate audience where it matters most. Perhaps this will be handled by clients, or by relays. One solution I’ve heard from people in the Nostr space is to just ‘spin up another nPub’ for your different audience. While I have no problem with people doing that - I have multiple nPubs myself - it’s clearly NOT a solution to the underlying problem here.
We’re experimenting with something. Whether it’s a good idea or not remains to be seen. Satlantis users will be able to curate their profiles and remove (hide / delete) content on our app. We’ll implement this in two stages:
Stage 1: Simple\ In the first iteration, we will not broadcast a delete request to relays. This means users can get a nicely curated profile page on Satlantis, but keep a record of their full profile elsewhere on other clients / relays.
Stage 2: More complex\ Later on, we’ll try to give people an option to “delete on Satlantis only” or “delete everywhere”. The difference here is more control for the user. Whether we get this far remains to be seen. We’ll need to experiment with the UX and see whether this is something people really want.
I’m sure neither of these solutions are ‘ideal’ - but they’re what we’re going to try until we have more time & resources to think this through more.
Next…
Nostr is not for Censorship Resistance
I’m sorry to say, but this ship has sailed. At least for now. Maybe it’s a problem again in the future, but who knows when, and if it will ever be a big enough factor anyway.
The truth is, while WE all know that Nostr is superior because it’s a protocol, people do NOT care enough. They are more interested in what’s written ON the box, not what’s necessarily inside the box. 99% of people don’t know wtf a protocol is in the first place - let alone why it matters for censorship resistance to happen at that level, or more importantly, why they should trust Nostr to deliver on that promise.
Furthermore, the few people who did care about “free speech” are now placated enough with Rumble for Video, X for short form and Substack for long form. With Meta now paying lip-service to the movement, it’s game over for this narrative - at least for the foreseeable future.
 The "space in people’s minds for censorship resistance has been filled. Both the ‘censorship resistance’ and ‘free speech’ ships have sailed (even though they were fake), and the people who cared enough all boarded.
The "space in people’s minds for censorship resistance has been filled. Both the ‘censorship resistance’ and ‘free speech’ ships have sailed (even though they were fake), and the people who cared enough all boarded.For the normies who never cared, they still don’t care - or they found their way to the anti-platforms, like Threads, BlueSky or Pornhub.
The small minority of us still here on Nostr…are well…still here. Which is great, but if the goal is to grow the network effect here and bring in more people, then we need to find a new angle. Something more compelling than “your account won’t be deleted.”
I’m not 100% sure what that is. My instinct is that a “network of interoperable applications”, that don’t necessarily or explicitly brand themselves as Nostr, but have it under the hood is the right direction. I think the open social graph and using it in novel ways is compelling. Trouble is, this needs more really well-built and novel apps for non-sovereignty minded people (especially content creators) and people who don’t necessarily care about the reasons Nostr was first built. Also requires us to move beyond just building clones of what already exists.
We’ve been trying to do this Satlantis thing for almost a year now and it’s coming along - albeit WAY slower than I would’ve liked. We’re experimenting our way into a whole new category of product. Something different to what exists today. We’ve made a whole bunch of mistakes and at times I feel like a LARP considering the state of non-delivery.
BUT…what’s on the horizon is very special, and I think that all of the pain, effort and heartache along the way will be 100% worth it. We are going to deliver a killer product that people love, that solves a whole host of travel-related problems and has Nostr under the hood (where nobody, except those who care, will know).
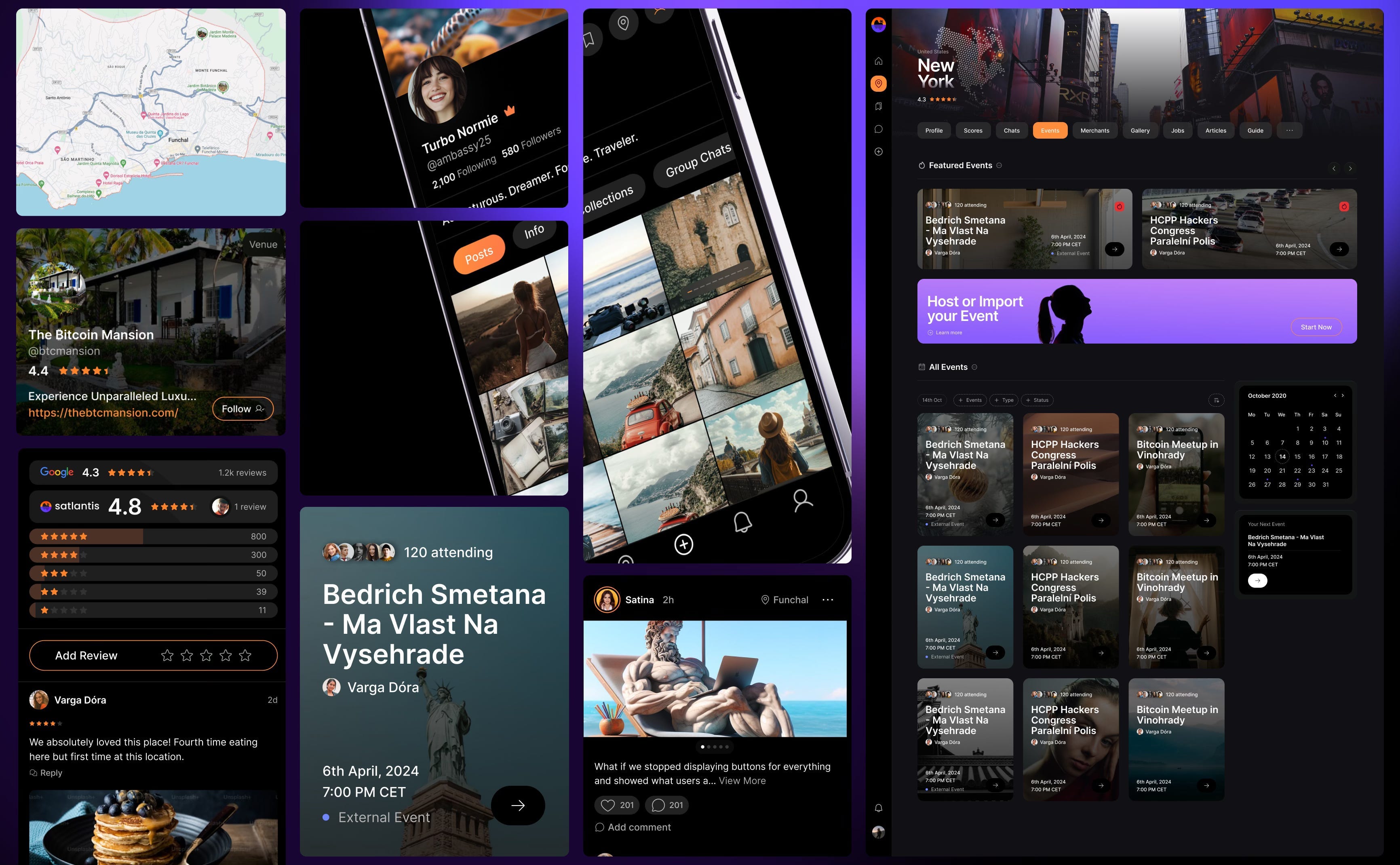
Grants come with a price
This one is less of an opinion and more of an observation. Not sure it really belongs in this essay, but I’ll make a small mention just as food for thought,
Grants are a double-edged sword.
I’m super grateful that OpenSats, et al, are supporting the protocol, and I don’t envy the job they have in trying to decipher what to support and what not to depending on what’s of benefit to the network versus what’s an end user product.
That being said, is the Nostr ecosystem too grant-dependent? This is not a criticism, but a question. Perhaps this is the right thing to do because of how young Nostr is. But I just can’t help but feel like there’s something a-miss.
Grants put the focus on Nostr, instead of the product or customer. Which is fine, if the work the grant covers is for Nostr protocol development or tooling. But when grants subsidise the development of end user products, it ties the builder / grant recipient to Nostr in a way that can misalign them to the customer’s needs. It’s a bit like getting a government grant to build something. Who’s the real customer??
Grants can therefore create an almost communist-like detachment from the market and false economic incentive. To reference the Nostr decision framework I showed you earlier, when you’ve been given a grant, you are focusing more on the X axis, not the Y. This is a trade-off, and all trade-offs have consequences.
Could grants be the reason Nostr is so full of hobbyists and experimental products, instead of serious products? Or is that just a function of how ambitious and early Nostr is?
I don’t know.
Nostr certainly needs better toolkits, SDKs, and infrastructure upon which app and product developers can build. I just hope the grant money finds its way there, and that it yields these tools. Otherwise app developers like us, won’t stick around and build on Nostr. We’ll swap it out with a better tool.
To be clear, this is not me pissing on Nostr or the Grantors. Jack, OpenSats and everyone who’s supported Nostr are incredible. I’m just asking the question.
Final thing I’ll leave this section with is a thought experiment: Would Nostr survive if OpenSats disappeared tomorrow?
Something to think about….
Coda
If you read this far, thank you. There’s a bunch here to digest, and like I said earlier - this not about shitting on Nostr. It is just an enquiry mixed with a little classic Svetski-Sacred-Cow-Slaying.
I want to see Nostr succeed. Not only because I think it’s good for the world, but also because I think it is the best option. Which is why we’ve invested so much in it (something I’ll cover in an upcoming article: “Why we chose to build on Nostr”). I’m firmly of the belief that this is the right toolkit for an internet-native identity and open social graph. What I’m not so sure about is the echo chamber it’s become and the cult-like relationship people have with it.
I look forward to being witch-hunted and burnt at the stake by the Nostr purists for my heresy and blaspheming. I also look forward to some productive discussions as a result of reading this.
Thankyou for your attention.
Until next time.
-
 @ 30b99916:3cc6e3fe
2025-03-14 15:11:18
@ 30b99916:3cc6e3fe
2025-03-14 15:11:18btcpayserver #lightning #lnd #powershell
In this article I'm going to go through basics of what it takes to implement a BTCPAY server instance on a VM cloud hosted computer or on your own computer. I've been running BTCPAY server now for about 2 years and haven't done much with it other than host an LND lightning node. After watching a BTC SESSIONS tutorial, this motivated me to do a little more with my BTCPAY server instance. A BIG Thanks goes out to BTC SESSIONS for getting me motivated again. Of course, none this would be possible without the grand contribution the BTCPAY server team as made. I take a knee to these giants before me.
**Step 1** is if you don't know anything about BTCPAY server then watching the BTC SESSIONS tutorial is a requirement.
Be aware that your being directed to use a one-click process for doing BTCPAY server installation these days, but this leaves one without the knowledge and experience needed to trouble shoot your own installation.
My old saying is:
"You can't learn how to ride a horse by watching someone else do it. You have to experience it for yourself".If you want to skip the experience, then this article is a waste of your time.
**Step 2** is to decide where to host your BTCPAY Server instance, self-hosting on your own hardware, hosting on cloud instance, or buy a node in the box solution that supports the installation of BTCPAY server. There isn't a wrong answer here so choose the option that works for you.
Initially, I started with the LunaNode hosting solution and later implemented a second instance on Oracle Cloud Infrastructure (OCI) because they offer an always free VM instance using the parameters below. I have yet another implementation of a full Bitcoin core and LND instance running on my home server.
Shape: VM.Standard.A1.Flex OCPU count: 4 Network bandwidth (Gbps): 4 Memory (GB): 24 Local disk: Block storage only (200GB)Currently, I'm still running the full Bitcoin core with LND but it has no active channels and it is only available via Tor. The OCI instance is still running strong and the LunaNode instance have been removed.
In the 2 years of hosting BTCPAY server with OCI, I've paid 0 hostings charges. Other hosting providers are charging close to $75 dollars per month for this type of configuration. You do have to use a credit card to reqister.
Oracle Cloud. The last I checked the always-free offer is still available.
If this is your first exposure to BTCPAY server, I recommend you create a new Linux VM just for the sake of gaining the experience of installing and configuring the software. Then implement your final solution on the hardware or hosting service of your choice.
Your are going to need a DNS name so here is one of many options available - noips.com offers a free Dynamic IP address or low cost for a non-nagging one.
Just to be different, I'm going to do things in reverse order just so you'll get a glimpse of a functional implementation before umbarking on the journey yourself. The link below links to my Point-of-Sales app running on BTCPAY Server hosted on OCI.
The BTC SESSIONS tutorial referenced above does a great of demonstrating how to do implement a Point-of-Sales app.
My LND Lightning node alias is SANJOSE_UBETCHA and you can go to mempool.space to lookup information on it, if desired.
Us small time lightning node operators need to band together if we are going to stand a chance at surviving. We can't compete on a liquidity basis but we can compete on a connectivity basis, if we herd together.
A warning to those considering running your own lightning node: It's a big club and your not in it. -George Carlin
At the time of implementing my BTCPAY server instance running a lightning node was the only option for accepting lightning payments. But, now with NWC you can use your own lightning wallet to receive and make payments in sats. You'll need to pay some sats to one the big club members to open a payment channel though. This is likely the cheaper route to take when all things are considered.
I'm seriously considering dumping my LND instance and maybe even lightning too. If Lightning is just turning into a big player game, I'm out.
Here are the core things that I configured with my BTCPAY server instance.
``` 1. A DNS name pointing to my Linux server.
a. securely configured Linux system Davide-btc has done great job of outlining the steps https://github.com/asyscom/Node-Security-Hardening-Guide-for-BTC-and-Lightning-Node-on-Ubuntu b. git cloning of the BTCPAY software. c. PowerShell installed because I want it. I'm not going to justify this.```
When I originally started this article, I thought it would be easy to just reference existing documentation to get the job done, but this information is being dropped in favor one-click installation. So the information below is from my old notes which may be outdated, so please let me know if something is incorrect or missing.
At this point, 1(a) and 1(c) should be completed and tested so only 1(b) is left to do. 1(c) is optional BTW.
Prove it: If you CAN'T answer yes to the following questions, don't proceed with installing BTCPAY server.
You can you ping your DNS name from a remote network? You can you ping your IP address from a remote network? You can ssh to either IP or DNS address and get a console session? Do you have root access on your linux system (sudo su -)?Here are my old notes on the steps I took for installing BTCPAY Server on a Linux server.
```
Login as root
sudo su -Create a folder for BTCPay
mkdir BTCPayServer cd BTCPayServerClone BTCPay docker repository & set environmental variables
git clone https://github.com/btcpayserver/btcpayserver-docker cd btcpayserver-dockerRun btcpay-setup.sh with the RIGHT AND DESIRED PARAMETERS
export BTCPAY_HOST="YOUR DNS NAME" < PUT YOUR DNS NAME HERE export NBITCOIN_NETWORK="mainnet" export BTCPAYGEN_CRYPTO1="btc" export BTCPAYGEN_ADDITIONAL_FRAGMENTS="opt-save-storage-s" export BTCPAYGEN_REVERSEPROXY="nginx" export BTCPAYGEN_LIGHTNING="lnd" < SKIP THIS ONE IF YOU DON'T WANT LND LIGHTNING NODE export BTCPAY_ENABLE_SSH=trueRun the setup script
. ./btcpay-setup.sh -i```
After setup process completes, it will take some time before the blockchain is fully in sync so don't PANIC.
Also, capture the console output generated from the setup script and save it to a text file for later recall about what it did.
Browsing to your DNS NAME should now greet you with the BTCPAY Web server interface. The excellent BTC SESSIONS tutorial can now guide you from here.
Next steps.
How is your opertional knowledge of Docker? If it is lacking you need to bone up on it. https://www.docker.com/
Here some useful things to know how to do with docker on your BTCPAY server instance.
List the BTCPAY server docker container services that are actually running and their version information.
ssh to your server sudo su - cd <to your BTCPAY install path> cd Generated cp docker-compose.generated.yml docker-compose.yml docker ps --format "table {{.ID}}\t{{.Image}}\t{{.Names}}" rm docker-compose.ymlList the logs for a given docker container service
``` ssh to your server sudo su - cd
docker logs --tail 100 btcpayserver_bitcoind the prior example lists all the container names that can be used with 'docker logs' command
```
To renew the SSL certificate restart the letsencrypt container
sudo su - cd <to your BTCPAY install path docker restart letsencrypt-nginx-proxy-companionHopefully, this illustrates why you need to be famliar with the docker commands.
BTCPAY Server Docs This is the official documentation source and I've just touched on a few of them.
BTCPAY Server Chat This is the official chat channel. Go here when you are stuck and need to ask the experts on BTCPAY server.
Now, I'm going move onto some of the automation stuff I've recently done with the REST Api(s) related to BTCPAY server.
BTCpay and BTCpayApi are two PowerShell scripts that I wrote to make use of the LND REST api and the Greenfield REST api.
Generally, speaking REST api(s) provide the ability automate many of the tasks assoicated with software packages like LND and BTCPAY server.
The BTCpay and BTCpayApi creation is a proof of concept work to determine if it can free me up from the daily grind of button clicking on the associated GUI applications to get the same work done. At this point, I'm finding great value in using these REST api(s).
You can refer to BTCPayApi to get the full details about these 2 scripts.
BTCpayApi sole function is to invoke the REST Api(s) and return PowerShell objects to the caller. BTCpay (the caller) is responsible for submitting the correct input to BTCpayApi and processing the returned PowerShell objects as desired.
One of the useful commands is showing the status of the current active channels as shown below.
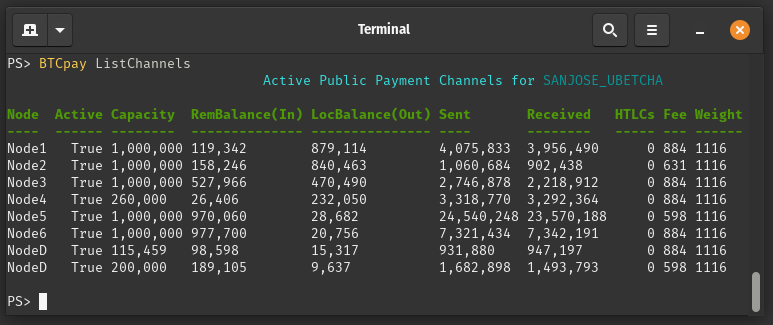
Another useful command is performing a Circular Rebalance between two active channels.
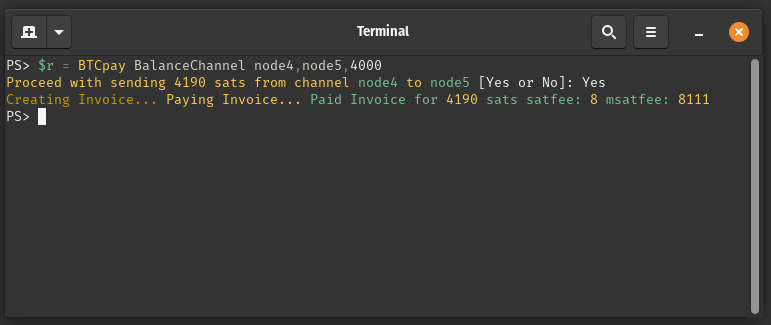
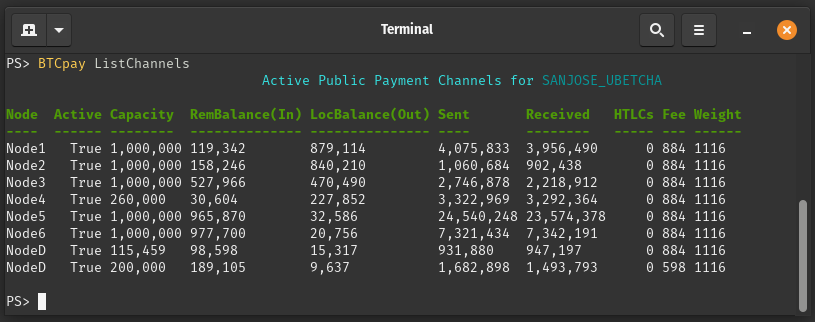
Notice how the channel balances have changed between Node4 and Node5.
The node names being displayed are aliases that I made up to replace their real alias names. There is an xml configuration file called, LNDnodes.xml that maps these alias names to their public key and chan_id.
One of the more difficult aspects of creating these scripts was ensuring that it did not leak sensitive data by embedding the values or keeping clear text data in a file. The current choices for protecting sensitive data are the key-value store implemented with Keybase, the key-value store implemented with Hashicorp Vault, and lastly the most laborious and error prone option is to input the data manually when prompted.
Each key-value store options comes with their own set of requirements. Since Zoom has purchased Keybase, the future of this application is unknown. In addition, Keybase is a centralized service so they could lock out your account on their whim. So, I'm going to focus on using the key-value store with Hashicorp Vault which has recently been purchased by IBM. The Hashicorp Vault solution that I'm using is totally self-hosted instance using the free download version. My corporate IT days provided me some exposure to this product and I never consider it for personal use until I discovered it had a REST api. Okay I said, "move over Web interface" here I come. The script, VaultApi totally automates all aspect of using Hashicorp Vault. See VaultApi for details.
Now with that history out of way, let's dive into configuring stuff in BTCpay/BTCpayApi.
The task at hand is to update the configuration file, BTCpayApiCfg.xml.
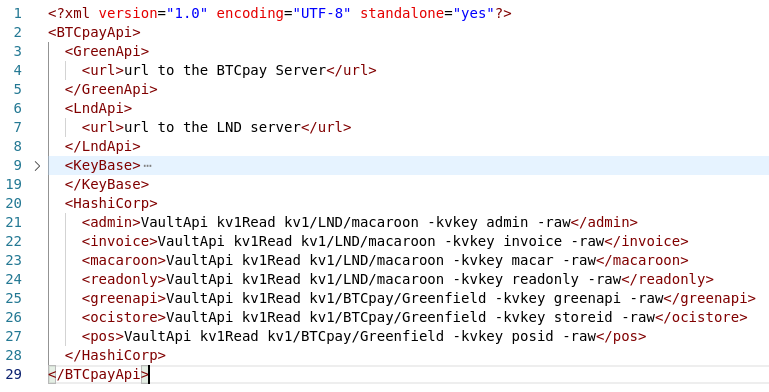 I've collaspe the Keybase section because I don't want it to be a distraction and no this is my real path information that I'm using.
I've collaspe the Keybase section because I don't want it to be a distraction and no this is my real path information that I'm using.Lines 4, 7, 21, 26, and 27 are the lines that need to be updated. The url format is, https://mydomain/quack/flap/
Looking a line 21, it is just executing the VaultApi script to go get the admin macaroon for LND.
It would be very trivial to implement support for any other password manager that supports either CLI and/or REST Api for retrieving data.
Hope this information has been of help. Thanks! for reading it.
-
 @ 7d33ba57:1b82db35
2025-03-27 09:25:04
@ 7d33ba57:1b82db35
2025-03-27 09:25:04Los Narejos is a laid-back beach town on the Costa Cálida, located in the Murcia region of Spain. Known for its calm, warm waters, family-friendly beaches, and proximity to the Mar Menor lagoon, it’s an excellent destination for relaxation, water sports, and enjoying the Mediterranean lifestyle**.
🏖️ Top Things to See & Do in Los Narejos
1️⃣ Playa de Los Narejos 🏖️
- A wide, sandy beach with shallow and warm waters, perfect for families.
- Palm-lined promenade for walking, cycling, or enjoying seaside cafés.
- Excellent for swimming, sunbathing, and beach sports.
2️⃣ Mar Menor Lagoon 🌊
- A unique saltwater lagoon, separated from the Mediterranean by La Manga.
- Warmer and calmer waters than the open sea, ideal for safe swimming.
- Known for its healing mud baths with minerals beneficial for the skin.
3️⃣ Watersports Paradise 🚤
- A top spot for kite surfing, windsurfing, sailing, and stand-up paddleboarding.
- Several local schools offer lessons for beginners and equipment rentals.
- Great conditions for kayaking along the Mar Menor coastline.
4️⃣ Promenade Walk to Los Alcázares 🚶♂️
- A scenic coastal walk from Los Narejos to Los Alcázares.
- Pass by chiringuitos (beach bars) serving fresh seafood and cocktails.
5️⃣ Local Markets & Shopping 🛍️
- Visit the Los Alcázares Market (Tuesdays & Saturdays) for local produce, clothes, and crafts.
- Small boutique shops sell Murcian souvenirs, ceramics, and wines.
🍽️ What to Eat in Los Narejos
- Caldero Murciano – A traditional seafood rice dish, full of flavor 🍚🐟
- Dorada a la Sal – Fresh sea bream baked in salt, a Mediterranean specialty 🐠
- Tapas & Mariscos – Try local seafood tapas like grilled prawns, octopus, and clams 🍤
- Pastel de Carne – A Murcian meat pie, perfect for a quick bite 🥧
- Paparajotes – A sweet treat made from lemon leaves coated in batter and fried 🍋🍩
🚗 How to Get to Los Narejos
✈️ By Air: The nearest airport is Región de Murcia Airport (RMU, 30 min drive).
🚆 By Train: Nearest station is in Balsicas (20 min drive), with connections to Murcia and Cartagena.
🚘 By Car: 30 min from Murcia, 1 hr from Alicante, 20 min from Cartagena.
🚌 By Bus: Direct buses from Murcia, Cartagena, and Alicante.💡 Tips for Visiting Los Narejos
✅ Best time to visit? Spring to early autumn (April–October) for great weather ☀️
✅ Try water sports – Mar Menor is one of the safest places for beginners 🏄♂️
✅ Bring a bike – The flat terrain and coastal paths are great for cycling 🚴
✅ Enjoy the sunset – The Mar Menor has some of the most stunning sunset views 🌅 -
 @ 3ddeea52:c0ef7371
2025-03-14 12:50:56
@ 3ddeea52:c0ef7371
2025-03-14 12:50:56Using the mempool.space API we can quickly fetch the most recent 99 blocks, and display useful information about recent blocks at a glance using a new visualisation approach.
Miners
We can colour code each block based on which miner found it, giving us a nice visual representation of the last 16h or so of blocks.

Mining Proxies
There is much debate and discussion around common block templates and possible proxy pools. For example, a quick look at the mempool stratum job visualiser at any random time will reveal that bunch of pools all sending the exact same set of transactions. We might want to see what the impact on block template diversity is if this example set of miners were acting as single group.
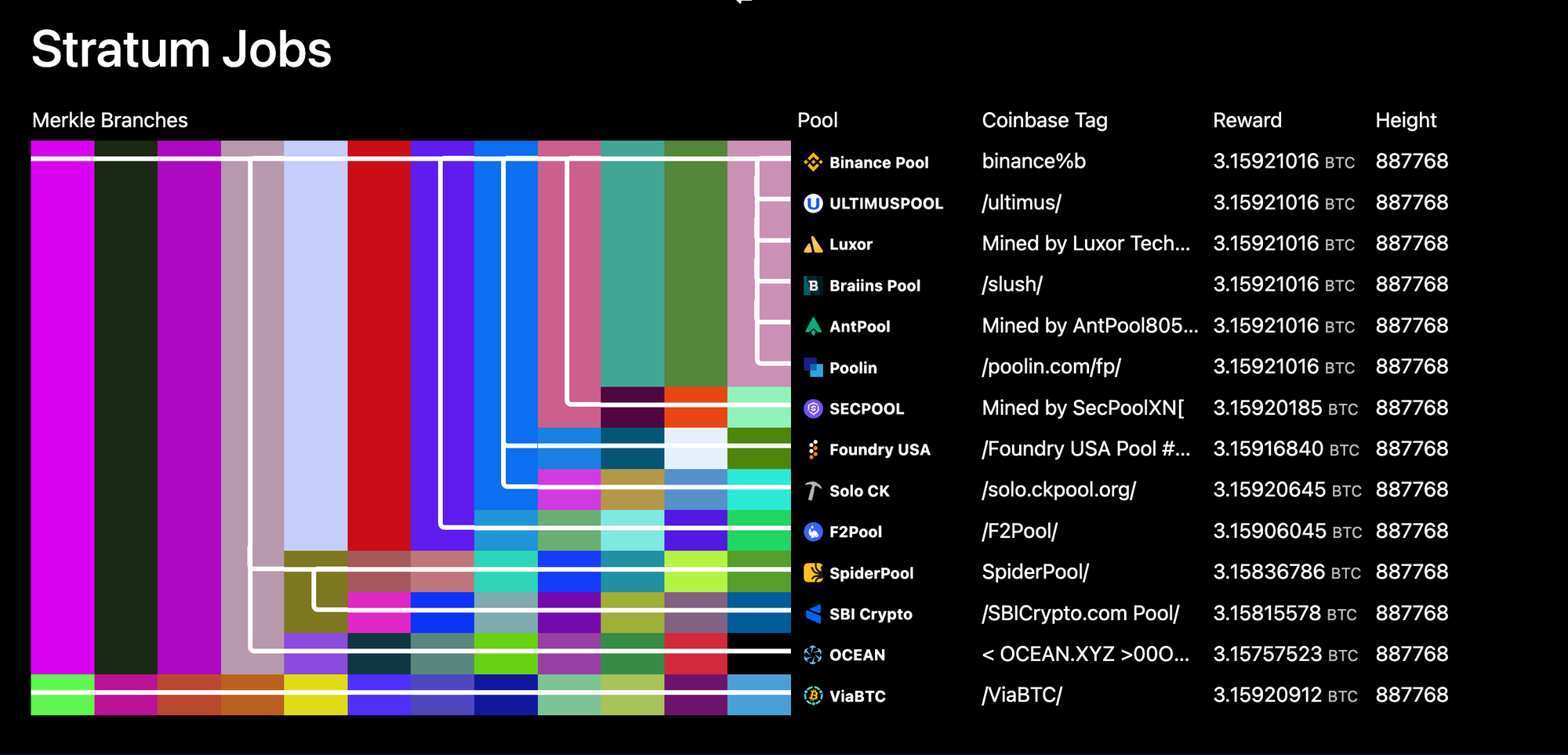 > Warning - A snapshot is not proof of a common template issuer - common tx sets in templates can occur naturally when the "churn" in the set of transactions in the next mempool block template is low (e.g. when there isn't much activity, especially just after a block was mined). For example see this screenshot below.
> Warning - A snapshot is not proof of a common template issuer - common tx sets in templates can occur naturally when the "churn" in the set of transactions in the next mempool block template is low (e.g. when there isn't much activity, especially just after a block was mined). For example see this screenshot below.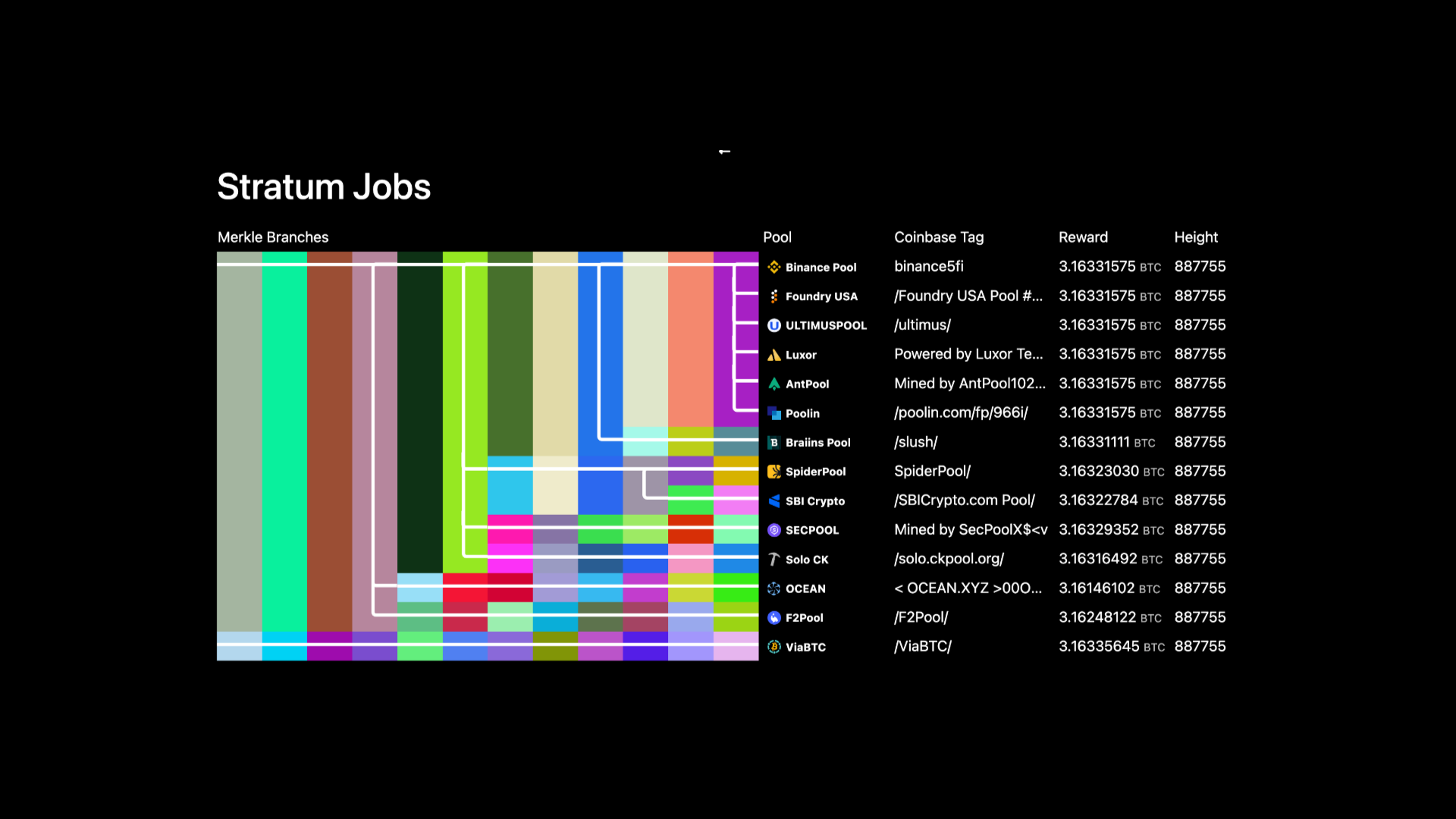
To explore the effect of a group, you can go to grid.orange.surf create a custom group, give it a name and select a custom colour for your group.
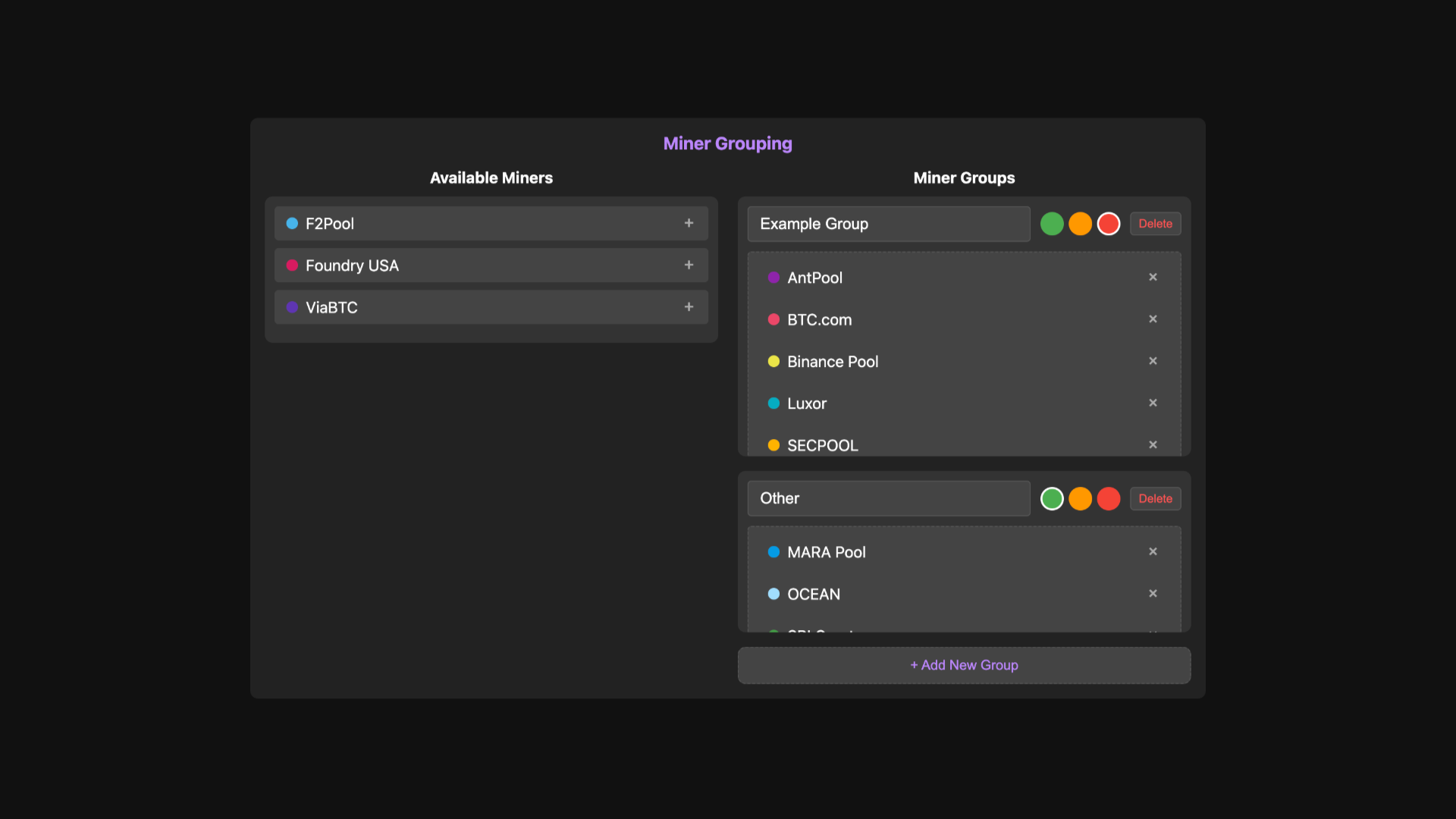 The block colour and legend auto update as you make changes, and all the info is stashed in the URL so you can easily share the link, this link\
\
Make your own groupings and share them in your blog posts on proxy pool speculation!
The block colour and legend auto update as you make changes, and all the info is stashed in the URL so you can easily share the link, this link\
\
Make your own groupings and share them in your blog posts on proxy pool speculation! 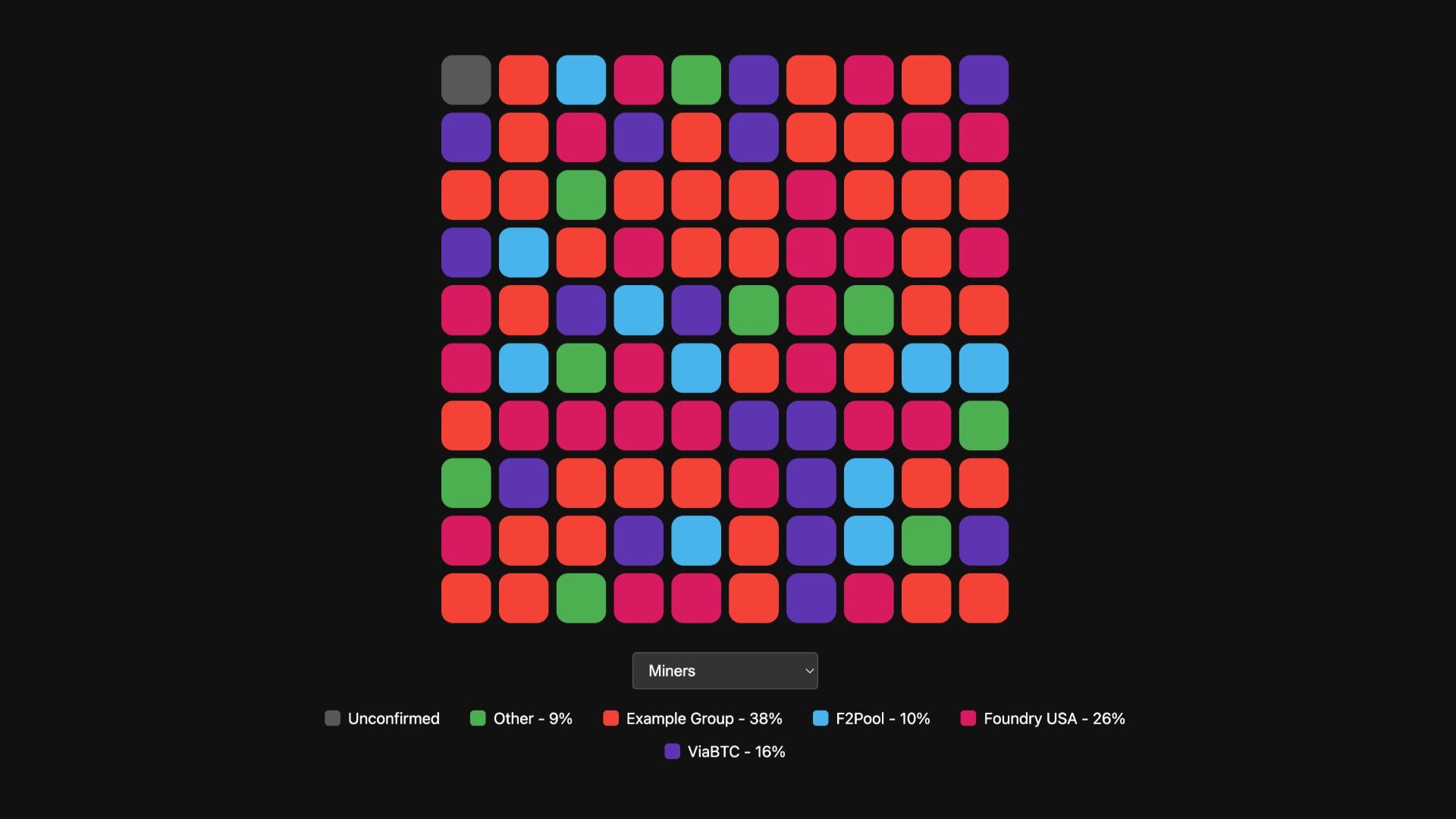 # \
Other Data
# \
Other DataWe can use this same visual approach to show other data at a glance
Fees
We can display the median fees rate, in this case we see that the recent fees have been low (5 sat/vB) with only occasional blocks with an elevated fee.
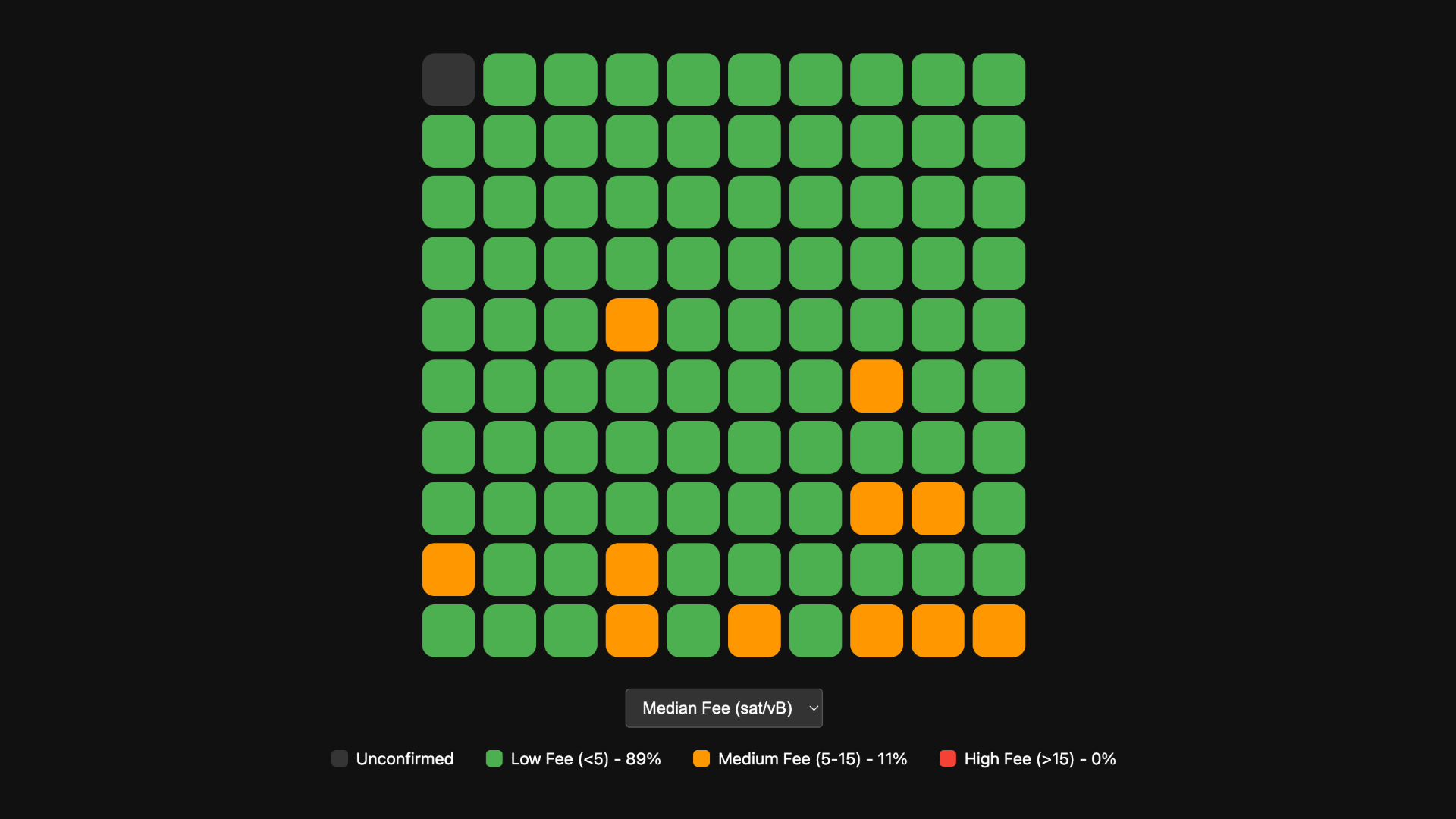 ## Transaction Count
## Transaction CountNext we have the number of transactions per block.
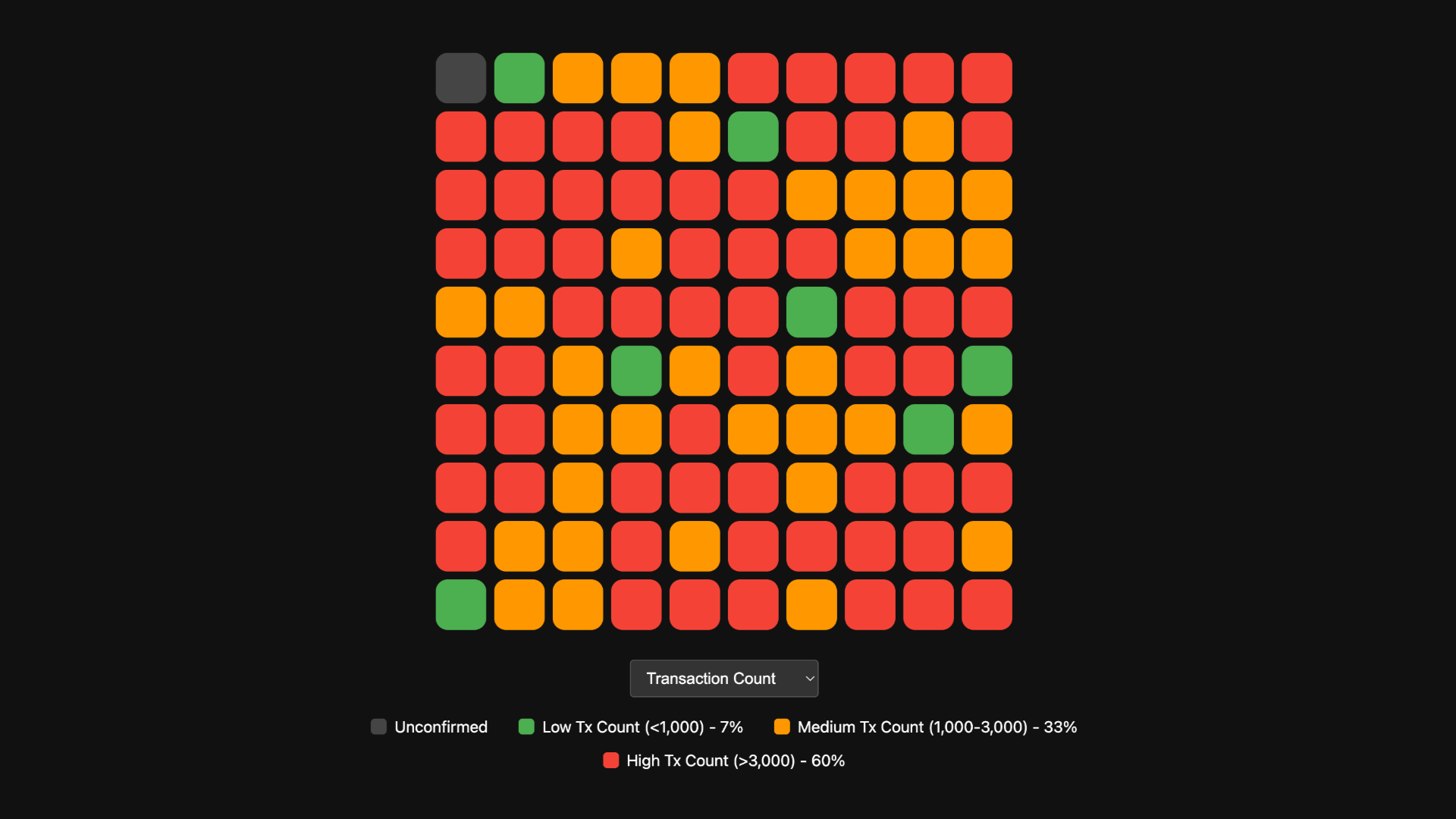
Block Weight
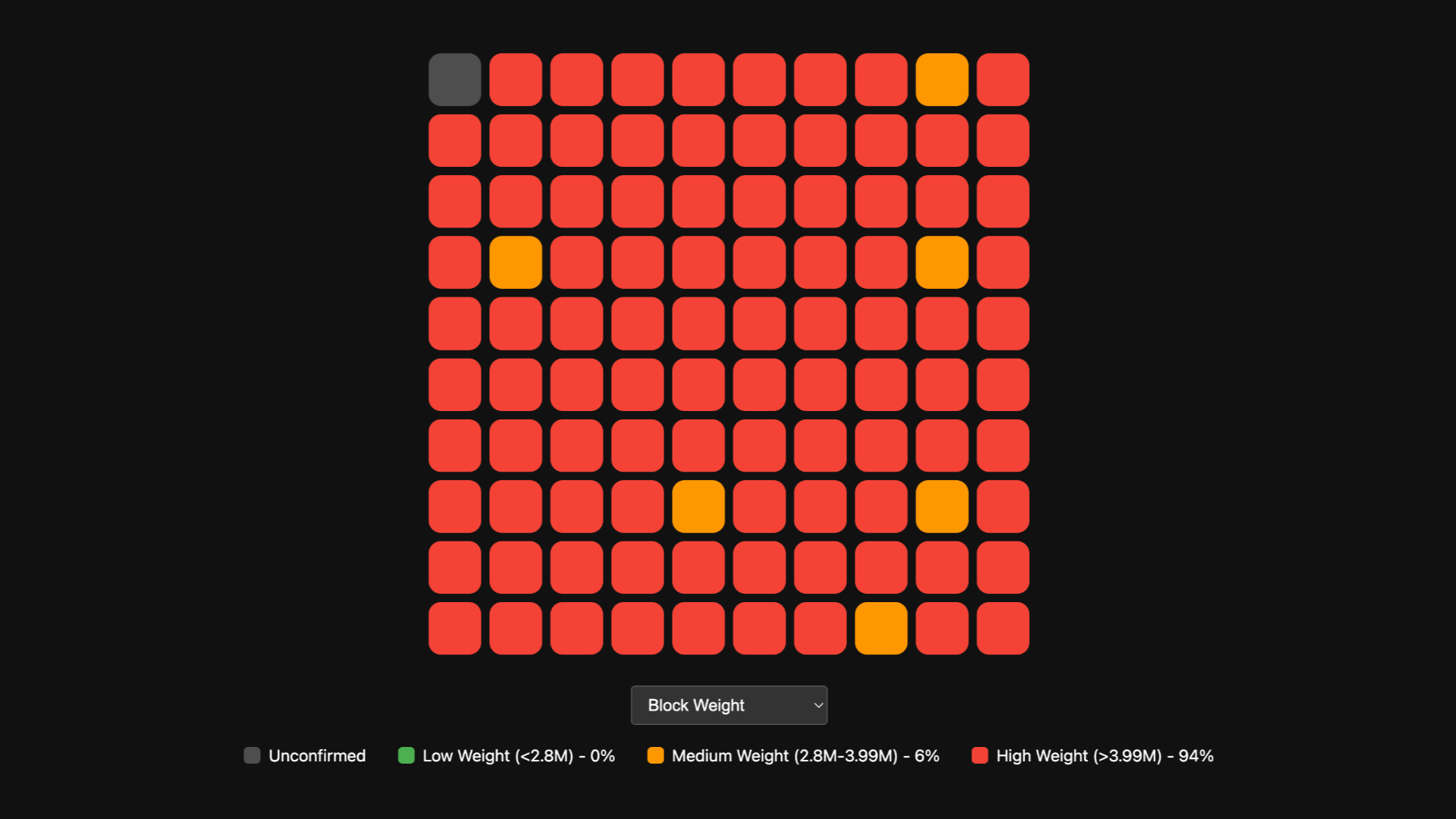
Other Features
Hover
On desktop we can hover over a block to see more information, such as the block height, the miner name etc. and clicking on the block opens it in mempool.space for deeper review.

If you enjoyed this and find it useful zap me some sats to buy me a coffee to keep adding new features like long-term visualisation of thousands of blocks and sorting by clusters.
-
 @ 866e0139:6a9334e5
2025-03-27 09:03:33
@ 866e0139:6a9334e5
2025-03-27 09:03:33Autor: Michael Meyen. (Bild: Hermine Zgraggen). Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Die Friedenstaube hat meine Kindheit und meine Jugend begleitet und wahrscheinlich auch beschützt. Ich bin auf der Insel Rügen aufgewachsen und sehe immer noch, wie der Bürgermeister am 1. Mai 1975 die US-Niederlage in Vietnam verkündete. Vielleicht war es auch der örtliche Parteisekretär. Egal. Der Sprecher stand jedenfalls am Heimatmuseum vor all den Fahnen, vor Sportlern, Pionieren und Erwachsenen, die mit ihren Kollegen durch das Dorf gegangen waren und jetzt auf den ersten Schnaps warteten. Ein Maiwässerchen, was sonst am Kampf- und Feiertag der Werktätigen. Ich Knirps war schon jetzt trunken vor Glück. Wenn ich einst groß sein bin, daran konnte es keinen Zweifel mehr geben, dann würde der Imperialismus besiegt sein und mit ihm der Krieg.
Was ist jetzt mit dem Sozialismus und seinem Frieden?
Picassos Friedenstaube war überall. Bei solchen Demos, in der Presse und in der Schule sowieso. Der Sozialismus, darauf schworen die Lehrer genauso Stein und Bein wie alle Funktionäre, der Sozialismus führt keinen Krieg. Es gab zwar immer wieder Gerüchte über Flussinseln, um die sich Moskau und Peking streiten würden, aber Asien war weit und China vielleicht nicht ganz so sozialistisch. Dann kam der Dezember 1979. Afghanistan. Ich war zwölf und konnte mir das schon deshalb nicht schönreden, weil es Olympia traf und damit zwei Sommerfernseh-Wochen. Was sind Goldmedaillen wert, wenn die Besten fehlen? Wenig später ging es um U-Boote. Ein Junge, nur wenig älter als ich, hatte an die *Ostsee-Zeitung* geschrieben, das Regionalblatt der SED, und gefragt, was die sowjetische Marine in schwedischen Gewässern mache und warum er sowas nur im Westradio hören könne. Als die Antwort kam, stand er mit dem Brief auf der Straße. Seht her, liebe Leute: Sie nehmen mich ernst. Was ist jetzt mit diesem Sozialismus und seinem Frieden?
Ich weiß noch, dass ich den Brief lesen musste (in der Schule wusste jeder, dass ich Journalist werden wollte), aber nicht mehr, was dort stand. Wahrscheinlich hat sich die Redaktion mit einem Missverständnis herausgeredet, mit Fake News oder mit Wilhelm Busch. Der Friede muss bewaffnet sein. Die Geschichte mit Igel und Fuchs gefiel mir. Da waren diese Zähne und damit die Drohung von Raubtier und Kapitalismus. Und da war ein eher zartes Lebewesen, das auf den Verstand setzte. „Und allsogleich macht er sich rund, zeigt seinen dichten Stachelbund – und trotzt getrost der ganzen Welt, bewaffnet, doch als Friedensheld.“
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
"Ich hasste das Militär"
Im Alltag war das nicht ganz so einfach, selbst für Kinder. Bei den Sportfesten hätte ich lieber einen Schlagball genommen als die F1, eine Handgranatenattrappe, die über die 35-Meter-Marke fliegen musste, damit der kleine Werfer überleben kann. Ich mochte die Soldatenspiele nicht, die alle paar Wochen angesetzt wurden, und schon gar nicht die Lager, die am Ende der Schulzeit warteten. Zwei Wochen in einer Baracke mit Frühsport in der Kälte und mit irgendwelchen Knallköpfen, die mir sagen konnten, was ich zu machen habe. Das heißt: Sie sagten das nicht. Sie brüllten. Und sie konnten jeden bestrafen, der nicht spurte. Ich hasste das Militär – und das nicht nur, weil ich nie sicher war, die Sturmwand beim ersten Anlauf zu nehmen und die Gasmaske schnell genug aus der Tasche zu haben.
Ich überspringe die drei Jahre, die ich Uniform getragen habe. In meinem Gedächtnis ist dort eine Leerstelle. Ich bin mir aber sicher, dass es schrecklich gewesen sein muss, und höre noch all die Stimmen, die vorher auf mich eingeredet hatten. Wenn du an die Uni willst, Michael, dann musst du dafür bezahlen. Dann musst du zeigen, was dir dieses Land wert ist und die Arbeiterklasse, die hier nun mal regiert und später auch dein Studium bezahlt. Gib uns einen Fitzel deiner Lebenszeit. Ich habe diese Stimmen verflucht und dachte, dass ich ihnen nicht entkommen kann. Heute weiß ich, dass das nicht stimmt. Ich wusste es schon im ersten Semester, weil neben mir Jungs saßen, die nur 18 Monate bei der Fahne waren und trotzdem einen Platz bekommen hatten. Dass die DDR kurz danach ohne einen Schuss zusammenbrach, habe ich nicht verstanden, aber trotzdem aufgeatmet. Du musst nicht mehr Reserveoffizier werden. Wenigstens das nicht. Die drei Lehrgangswochen habe ich in der Pathologie des Uni-Krankenhauses verbracht, vermutlich mit irgendwelchen Aufräumarbeiten.
Eine Wette mit meinem Sohn
Mein Sohn ist 1995 zur Welt gekommen. Ein Stammhalter. Ein Brüderchen für unsere Tochter. Aber auch ein Soldat. Ich habe mit mir selbst gewettet, dass es keine Armee mehr geben würde und vor allem keine Wehrpflicht, wenn er 18 ist, und geschworen, dafür alles zu tun, was mir möglich ist. Dass es dann dieser Minister von der CSU war? Was soll’s, dachte ich. Hauptsache, der Junge kann selbst entscheiden, wo und wie er in die Erwachsenenwelt gehen will.
Damals war ich mir sicher: Bertolt Brecht hat gewonnen. Endlich weiß Deutschland, dass es nicht Karthago sein will. Jetzt schreibe ich für die Friedenstaube und würde diesen Brecht lieber heute als morgen auferstehen lassen. So schwer kann das doch nicht zu verstehen sein mit den drei Kriegen.
Michael Meyen, Jahrgang 1967, hat an der Sektion Journalistik studiert und dann in Leipzig alle akademischen Stationen durchlaufen: Diplom (1992), Promotion (1995) und Habilitation (2001). Parallel arbeitete er als Journalist. Seit 2002 ist Meyen Professor für Kommunikationswissenschaft an der LMU München. Er hat drei interdisziplinäre Forschungsverbünde als Sprecher geleitet: "Fit for Change" (Laufzeit: 2013 bis 2017), "Zukunft der Demokratie" (2018 bis 2022) und "Das mediale Erbe der DDR" (2018 bis 2025). Mehr zum Autor und seinen Büchern hier.
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ b90c3cb7:1be67823
2025-03-14 11:33:12
@ b90c3cb7:1be67823
2025-03-14 11:33:12This guide uses cashu.me and the 0xchat app
First go to cashu.me. Make sure you've added a mint. I suggest mint.0xchat.com (note for newbies like I recently was, it's the number zero and not the letter O). Make sure you have some balance. Then hit SEND and choose ECASH.

Next type in a small amount to send. As always with bleeding-edge stuff accept the token can go poof. Only after you've typed in a number will you see the LOCK button appear next to the SEND button.

Hitting LOCK will reveal the "Receiver public key" field as below. This works for public keys generated within cashu.me (go to cashu.me settings) as well as for Nostr public keys.

Next copy your own public key (or that belonging to whoever you want to test this with) and head over to https://nostrcheck.me/converter/ and paste it in there. This will convert it to hex format, which is needed in this case.

After that go back to cashu.me and paste the hex format key in that field. It'll be in this red color "Invalid public key" state, don't worry.

Add 02 (number zero, number two) in front of the hex key. That'll make it valid. It's just the scheme. You'll see the locked icon appear next to the SEND button.

Then hit SEND and, voila, you now have a Cashu token that only the person in control of the nsec of whatever public key you used just then can redeem. Post it publicly to taunt others. (FYI the P2PK abbreviation there means pay-to-public-key.) Hit COPY to grab the token string.

Last up, open 0xchat. Assuming you're doing this yourself, make sure you're logged in with the nsec of the public key you used to create the test token. Also make sure the token string resides in the clipboard of the device you're using 0xchat on.

Then go to th "Me" tab in 0xchat to open the Cashu wallet. Set it up if you haven't already. Hit "Receive" and then "Redeem Ecash". As long as the token is in your clipboard and you did it all the steps right it should be redeem straight to your Cashu wallet. Well hopefully.
That's it. This guide will self-descrut if it goes out of date or was wrong somehow.
-
 @ 7d33ba57:1b82db35
2025-03-27 08:55:21
@ 7d33ba57:1b82db35
2025-03-27 08:55:21L'Estartit is famous for its stunning beaches, the Medes Islands, and incredible diving opportunities. Once a small fishing village, it’s now a paradise for nature lovers, water sports enthusiasts, and those seeking a relaxing Mediterranean escape.
🏖️ Top Things to See & Do in L'Estartit
1️⃣ Medes Islands (Illes Medes) 🏝️
- A protected marine reserve, perfect for snorkeling and scuba diving.
- Explore sea caves, coral reefs, and diverse marine life.
- Take a glass-bottom boat tour to admire the underwater world without getting wet.
2️⃣ L'Estartit Beach 🏖️
- A long sandy beach with shallow waters, ideal for families.
- Great for swimming, sunbathing, and water sports like windsurfing and kayaking.
- Offers fantastic views of the Medes Islands.
3️⃣ Montgrí Massif & Castle 🏰
- Hike up to the Montgrí Castle for panoramic views of the Costa Brava.
- Trails through rocky landscapes and Mediterranean forests.
- A perfect spot for hiking, mountain biking, and photography.
4️⃣ Coastal Walking Route (Camí de Ronda) 🌊
- A breathtaking hiking trail along the cliffs, connecting L'Estartit with nearby beaches and coves.
- Discover hidden spots like Cala Pedrosa and Cala Ferriol.
5️⃣ Explore the Old Town & Port ⚓
- Wander through narrow streets with local shops and seafood restaurants.
- Visit the Sant Genís Church, a historic landmark in the town center.
- Enjoy a drink with a view at the marina.
6️⃣ Kayaking & Stand-Up Paddleboarding 🚣♂️
- Paddle along the coastline to explore caves, cliffs, and hidden coves.
- A great way to experience the natural beauty of the area.
🍽️ What to Eat in L'Estartit
- Suquet de Peix – Traditional Catalan fish stew 🐟
- Arroz a la Cassola – A savory rice dish with seafood 🍤
- Fideuà – Like paella, but made with short noodles instead of rice 🍜
- Calamars a la Planxa – Grilled squid with olive oil and garlic 🦑
- Crema Catalana – A classic Catalan dessert similar to crème brûlée 🍮
🚗 How to Get to L'Estartit
🚆 By Train: The nearest train station is Flaçà (30 min by car/taxi) with connections from Barcelona and Girona.
🚘 By Car: 1.5 hrs from Barcelona, 45 min from Girona, 1 hr from Figueres.
🚌 By Bus: Direct buses from Barcelona, Girona, and other Costa Brava towns.
✈️ By Air: The nearest airport is Girona-Costa Brava (GRO, 55 km).💡 Tips for Visiting L'Estartit
✅ Best time to visit? Late spring to early autumn (May–September) for warm weather 🌞
✅ Book diving tours in advance – Medes Islands are a top diving destination 🤿
✅ Hike early in the morning to avoid the heat & get the best views 🥾
✅ Visit in June for the Havaneres Festival, celebrating Catalan maritime music 🎶 -
 @ 6f0a6a19:7dd662db
2025-03-14 07:20:00
@ 6f0a6a19:7dd662db
2025-03-14 07:20:00I have been on a mission to make bitcoin physical longer than I would like to admit. And I mean really physical—not like the physical key cards or flash drives that hackers can exploit and governments can censor. I’m talking about a type of cypherpunk alchemy that incarnates the unit of account into physical material.
This obsession took root when I realized how close we are to the cashless society so many science fiction writers and futurists warned us about. At first, I thought this transition was an inevitable product of the free market. However, in my career as a digital assets journalist, I learned that there is more freedom at stake than we realize. The lack of financial privacy isn’t simply a bug in digital asset payment networks. It is a surveillance feature that the network state will do anything to preserve. For example, the government sanctions against privacy tools like Tornado Cash, its seizure of privacy-enhancing wallet servers like Samourai wallet and its forced delisting of privacy coins like Monero demonstrate that this system has no tolerance for financial privacy. These inherent anti-privacy objectives made me realize that the only way to protect my right to privacy was to find a way to cash the first and most recognized decentralized digital asset out of this surveillance matrix and into physical instantiations that are independently verifiable. Any other digital solution would be too vulnerable to state-authorized enforcement policies.
It took some time and a life-altering injury to open my mind, but eventually, I discovered a way to make this a reality. I developed a procedural standard for minting bitcoin into physical material and published it to the digital asset’s blockchain. This minting standard is like a peer-to-peer ATM. It requires no central organization or manufacturer and is open to anyone. But before I explain how it works, I want to explain why you should care that cash is on the way out.
 You can find copies of this guide with physical bitcoin at local bookstores around LA.
You can find copies of this guide with physical bitcoin at local bookstores around LA.THE CONTACTLESS NETWORK STATE
Physical cash doesn’t simply offer access to privacy. It gives you the freedom to cooperate with whomever, and however, you like in the marketplace. That physical exchange of tendered goods and services establishes social relationships of mutual respect. They come with body language and a face that other human beings can recognize, appreciate and hold accountable.
This lack of intermediation in cash makes room for moments of spontaneous exchange in ways that digital payments do not. For example, if you are walking down the street with cash in your pocket, you might consider checking out local vendors at the farmers market. You might give it to someone in need or stop by your favorite food truck. These moments of unmediated cooperation may not feel like much, but they condition us to see people outside our immediate social circle as members of the same social organism.
Digital transactions, both in person and not, defer the responsibilities of recognition and accountability to a matrix of automated protocols and machines. They make it possible to conduct business without ever interacting with the other party to the exchange. This system is like putting training wheels back on a bike. Over time, you slowly forget what it is like without them.
Besides removing the opportunity for moments for spontaneous exchange, the ecosystem for digital payments substitutes social connection with people and content that better affirm our individuality. This system creates a toxic feedback loop that keeps people in a matrix of increasing automation. Think about it. How many purchases from the past month were made because an algorithm suggested them while connecting you to the content and people that best serve your interests? This experience not only puts sales associates out of business; it makes them a literal deterrence from shopping in person. Customer surveys have shown that a simple question like, “can I help you with anything?” feels “pushy” and is an unwanted social interaction. If you would like more research on this subject, I recommend reading “The Extinction of Experience” by Christine Rosen. She masterfully explains the total impact that these intermediating forces have on society.
But the point I wish to make here is that the transition away from cash, amidst this societal shift, is giving up more agency and mutual good than we realize. Whatever financial freedoms we enjoy now only exist because we have a non-surveillable option we can use if we need to.
Physical cash represents our bargaining chip against the banking and corporate class. But the network state is working hard to remove that chip from the table. Those "no cash" signs you see at more and more coffee shops are just the tip of a well-constructed mechanical spear aimed squarely at the human-to-human exchange.
THE WAR AGAINST PHYSICAL MONEY
Over the past 5 years, banks have doubled business cash deposit fees and increased all other costs associated with running a cash-heavy operation—making it more expensive than digital payment solutions. That coordinated effort, along with the help and political influence of organizations like The World Health Organization and Better Than Cash Alliance, has made refusing cash not only socially acceptable and financially expedient but they have made it a virtue of "sustainable development." This rebranding and the cachet businesses earned for requiring contactless payments during COVID-19 gave them the cover needed to continue the practice today. As a result, the number of companies no longer accepting cash is at an unprecedented all-time high of 40%.
This effect is not the result of a secret cabal. It is what the techno-optimists hail as the grand "network effect." It is the culmination of incentives that orient banking, government and UN-backed systems toward increasing automation and intermediation. As I pen this essay, Congress is discussing a stablecoin bill that would allow the executive branch to eliminate cash altogether. The bill in its current draft enables the infrastructural changes needed for a cashless upheaval because it introduces a novel interbank accounting trick. It would let banks fund their operations with self-issued stablecoins backed with deposits at partner banks. The bill itself doesn't explicitly sanction this practice, but it does create exploitable loopholes to its effect. In short, it enables the same type of hidden leverage and circular financing that fueled the 2008 mortgage-backed security crisis, and it creates a regulated substitute that they can use to replace cash.
If the bill passes, we are only one more financial crisis and emergency powers directive away from all banks closing their cash ATMs in turn for their freshly minted, surveillable and programmable stablecoins.
THE CASHLESS CONTINGENCY PLAN
With the looming US debt crisis, the timing of this bill suggests that this might be the work of a contingency plan for when the US government no longer has the political will to service its debt. You see, the Treasury and Congress are between a rock and a hard place. The cost to service the government's debt just surpassed the defense budget. And it will soon overtake and compete with Social Security and Medicare. Congress must either make room for the debt by making severe cuts to the budget or issue new debt to pay the old. The latter option is getting more difficult because the Federal Reserve needs to keep the cost of issuing debt high to curb inflation. And the economy and political will doesn't seem strong enough to make the necessary cuts for the debt payments. The only other option is refinancing the debt with key creditors like China and Russia.
In this scenario, the US would face a different existential crisis. Because the interest that one receives for holding US debt is the only reason the world is interested in holding its Dollar. There is nothing else backing US currency. So, if the government renegotiates its debt, it would need a system to ensure and secure interest in the US Dollar.
Historically, governments have fixed a currency exchange rate for gold and/or silver to secure this interest in their currency domestically and abroad. However, these metals' physical portability and untraceability make anticipating and regulating redemption difficult. For example, the type of gold liquidity crunches that plagued the late 19th century and early 20th crippled the US banking system and subjected the economy to prolonged and difficult depressions. This is why, amid the Great Depression, Franklin D. Roosevelt issued an executive order to confiscate the public's gold.
To avoid losing its monetary power and flexibility, the US government will discover that it needs to secure its debt with a digital asset it doesn't directly control but can instantaneously monitor and mark individual units with approval or disapproval. And they will need a digital dollar that its citizens can’t take out of their surveillance state. This level of oversight would give them the ability to not only set an exchange rate that can price the new asset at a level that can adequately service their debt, but it also gives them the ability to set a punitive exchange rate for units of the reserve digital asset not redeemed at approved custodians. This carrot and stick incentive structure would provide the global dollar debt market insurance against the type of liquidity problems it faced when it was backed by gold and issued as physical Federal Reserve Notes.
Bitcoin is the only digital asset that the regulating powers can use to support this new monetary standard and system of control. First, it is the one asset secured on a universal public ledger with the longest record of distributed consensus value. Second, its public accounting record allows central authorities to track and devalue coins used for things or ways that don’t serve their interests. This asset’s transparency and historic primacy among all other digital coins make it an unbeatable state reserve asset. And so any currency not priced against it will eventually give way to a standard that is. This simple fundamental reality is undoubtedly why a bill to establish a strategic Bitcoin reserve is currently in Congress. The plan to hold bitcoin now can very well provide the precedent to reprice the dollar to a fixed exchange with bitcoin when the time comes. And the US isn’t the only one. Nation-states around the world are facing the same debt problems. These countries are racing to accumulate Bitcoin to their reserve now because they likely suspect others will need to reprice their currencies against it. El Salvador and Butan were the first to announce their reserves. But others like Brazil, Russia and Germany all have indicated that they are moving toward that direction.
A transition to such a standard will enrich many people holding bitcoin today. And it may avoid a prolonged global economic depression. But the trade-off will come at a grave cost. It will not only eliminate cash. It will further funnel the remaining energy reserved for in-person cooperation to this machine and the digital world in which it proliferates. And its expansion of power will make us more subject to coercion by exclusion. For example, suppose your credit to society is constantly monitored and validated by this Bitcoin-based matrix. In that case, your behavior is implicitly subject to its interests. Its most potent intelligence-gathering center will exercise this power by setting exclusionary restrictions on those less creditworthy and privileges to those who are more. These credit lines already exist and have, for a long time, created artificial boundaries between people, places, and things. But if we trade more and more of our lived experience for a system that can automate the enforcement of these lines, they will spread like the numbing venom of a parasite, transforming humanity into an empty host. We will exist as a means to something else’s end. Not someone else’s end, but a thing, an immaterial system of things bound by the predetermined objectives of a ghost.
Many people who follow this industry are well aware of this threat. But the only response they can give is that tech billionaires like David Sachs, Howard Lutnick, Peter Theil, and Elon Musk are spearheading this initiative, and it seems they have good intentions. If you want a well-rounded and good-faith argument for this perspective, listen to Adam Curry's explanation of the Stablecoin bill on the Joe Rogan Podcast. Personally, I find the “trust me bro” argument unconvincing. And then if you want a deep dive investigation into the motives behind these tech entrepreneurs, I recommend Whitney Webb’s reporting. The technocratic aims of these figure heads are well documented.
THE BITCOIN MINT
At this point, it is hard to imagine cash surviving past the next four years, let alone a decade. The cashless society of a digital matrix feels unavoidable. And honestly, the current state of online culture, with its personality cults, clout chasers, and reactionary communities, does not make this new digital age appear that golden.
Plenty of articles and documentaries attempt to warn the world of this growing separation. But these warnings, while alarming, fail to compel actual change. The small remnant of stubborn anarchists and luddites can't return society to material reality. Instead, these artists and commentators unwittingly feed the machine more attention by creating a market for techno-alarmist content. This market creates more financial and social capital incentives that pull collaborative energy away from other humans in the here and now. This irony doesn't discredit their points or invalidate their work. But speaking from experience, the irony is hard to swallow.
At first glance, it seems that we can't exit the system without isolating ourselves from society, and we can't try to convince others to leave the system without strengthening it.
This social predicament is like a Chinese finger trap. The harder you rage against it, the stronger it gets. So intuitively, the only way out is through. The Bitcoin Mint is how you and I can cash the value of our work in and out of this system. And it's a way we can speak to broader society without feeding the machine our attention. Here's how it works.
At face value, it is a set of procedures that offer the Bitcoin Network a way to concede that bitcoin sent to addresses derived from one-of-a-kind physical material is irreversibly minted into those objects.
When I first discovered this possibility, a friend asked me a question you are probably asking now. He could foresee how a genuinely one-of-a-kind object could correspond to frozen individual units of bitcoin, but he wanted to know how such a procedure could import bitcoin into physical material.
It's a great question. However, it presupposes that bitcoin exists as an identifiable thing in digital space. This is not the case, and it is a common misconception. Bitcoin is accounted for on a shared ledger in digital space, but it does not exist there, just as gold doesn't exist in the markings recorded on a balance sheet. That might throw you. So, let me give you a quick refresher on the Bitcoin basics.
Bitcoin's ledger isn’t the complex accounting system most assume it is. The ledger is only composed of three columns. The middle column accounts for the total supply of bitcoin, the far left denotes the location of each base unit of bitcoin, and the far right shows the record of change. This ledger has some rules and guidelines for making changes to this ledger that can get pretty technical, but conceptually, it doesn't get more complicated than those three columns.
Nowhere in that ledger or set of mutually held rules is there anything that actually defines the bitcoin recorded in the middle column or limits it to what it can and cannot become. It only limits the supply to 21 million bitcoins, with each bitcoin consisting of 100 million base units. The question, therefore, is not, how do you import bitcoin into physical material? It is; how do you ascribe a definition to the unit recorded to its middle column? And where on its ledger can you record that definition?
This question sent me down a curious thought experiment in a park in West Hollywood. You can't universally ascribe a definition at the top of the ledger because there is no way to ensure that each address owner will concede to abstract principles about the nature of the asset. And secondly, if the network could put forth a vote, there would be no way to prevent a vote to change it in the future.
The question about its definition is why every attempt to explain "what it is" is never the same. Some argue that it is the energy it costs to acquire, hash rate, computing power, digital property, currency, etc. No matter how adamant someone is, the answer is never consistent.
The only other option is to define bitcoin, one base unit at a time. But then the question becomes, where and how do you ascribe that definition to the ledger? At first, I thought one could theoretically ascribe that definition to the right side—the one dedicated to the record of change.
This record includes every detail associated with a transaction. But it also has a memo line for extra data. The ledger's consensus rules only limit the size of the data. So the contents can be anything we want. Many use this space to catalog things like article headlines, digital images and entire coding libraries. I initially thought that I could ascribe the definition to individual units of bitcoin by attaching a photo and message claiming that the bitcoin included in its transaction is defined by the material in the image.
But this definition doesn't hold true if the bitcoin in question can move to another destination address that isn't associated with that image. I realized that this type of actualization required sacrifice. It needed to sacrifice the potential for the accounted bitcoin to be anything other than this one thing in material reality.
This definition would not only need to prove that its bitcoin could never change destination addresses again. It would need to prove that the anchoring destination address was not a random string of numbers in abstracted digital space but, in fact, a verifiable expression of that object. Otherwise, that ambiguity would sever the connection between the bitcoin unit's unique expression in time and space with its ascribed location. It would be like saying my body is sitting in a 1990 Toyota Pickup, but my soul is elsewhere.
The procedural minting standard for The Bitcoin Mint meets this requirement. First, this standard is recorded on the right column of the bitcoin ledger under Satoshi Number: 1632665171305931. So anyone can reference it, and no one can alter it. Second, it offers free image detection software to create final destination bitcoin addresses derived from natural visual patterns. The public inscription of this software demonstrates, to those with a basic understanding of cryptography, that no one can ever send that bitcoin to another address. (For crypto nerds: The script proves this because it does not use public-private key pairs when creating the addresses.)
Those who wish to mint bitcoin into physical material must find a natural object with a unique, one-of-a-kind pattern and upload an image of it to the software. Then, they need to send bitcoin to the address created from the object. This transaction, with reference to The Bitcoin Mint, will forever ascribe this definition to the ledger's left column, proving to anyone who can see the physical material that the amount of bitcoin in question can only ever be the object from which its address was derived.
This minting standard transforms every single unit of bitcoin into little bits of a giant blank canvas. Every artistic contribution to that canvas is independently verifiable—meaning you don’t need an issuer or third party to authenticate it on your behalf.
To verify first, visually inspect that its natural irreproducible pattern matches "The Natural Standard" (the image used to generate the address). Second, run the Natural Standard image through "The Minting Standard" protocol to verify it generates the same result. This proves that there was no way to authenticate an outgoing transaction from the address and that the address was deterministically derived from the object in question. Lastly, verify that the bitcoin minted to the object is accounted for at the same address on the network. This step verifies that bitcoin was actually minted to the object and it tells you how much it is worth. I call this last verification step the "The Money Standard" because it ascribes something universal to all money; a way to measure its applied value.
WHAT NOW
Now, you are probably thinking, "the coffee shop down the street refusing to take cash will certainly refuse physical bitcoin. What does this solve?" And it's a good point. The simple existence of physical bitcoin won't change society or reverse this slow march into the digital matrix. But I didn't publish The Bitcoin Mint with this over-inflated notion that it will or must change the world. I published it because I wanted a way for my community to cash in and out when we want and how we want. I did it because, even though cash exists now, it probably won't soon. And I did it to make art that can redirect attention from the matrix toward the here and now.
The Bitcoin Mint doesn't need convincing or grand adoption to work. It is simply an inscription that shows you something. It unveils the garment of indescribability cloaked around Bitcoin's base units. What we do with that revelation is up for debate. You can use it to make bitcoin a canvas for your physical art. You can use it to hold and exchange bitcoin privately. You can even oppose this revelation with a religious devotion similar to the iconoclasts of old.
That discussion and debate is the most exciting element of this project. Because I alone can't tell you what to do with it. I can only show you my works. And you can only show me yours. This discovery invites a dialectic discourse of creativity and cooperation that demands to be seen in the here and now.
My work in all of this is to preserve the tension between organic cooperation and competition. Anarchists like Peter Kropotkin described this tension as mutual aid. It's the force that underpins and sharpens the collective efforts of every economic model throughout history. Automating that dialectic only weakens our resolve and makes us more pliable to the system mediating it.
And it's why making bitcoin physical isn’t my end goal. Because at the end of the day, while rudimentary as it is, physical bitcoin is still a mediating tool. We can easily make it a slip of credit that affirms our self-individuality over a gift that can affirm the works of one another. It's why I made the distinguishing mark on my physical bitcoin a hand of aid. I want this revelation to remind people of their innate instinct to cooperate.
EXCHANGING IDEAS
So, in that vein, I'm hosting a regular in-person meet-up for this conversation, debate and art exchange. It's not a podcast or substack. It's just a handful of creatives and critics wanting to learn more about bitcoin, credit, mutual aid and true anarchy. The plan is to publish this guide with the in-person feedback from this meet-up to The Bitcoin Mint Press—a nested catalog within The Bitcoin Mint. This meet-up and publishing system has the potential to branch off into other publishing and distribution hubs. But for now, it's a single hangout in space and time. (You can find more details about this in the link tree.)
You might ask, if the goal is to cultivate local cooperation and exchange, then why bother publishing anything at all? We forget that a publisher's work wasn't always an attempt to exploit your attention for personal gain. Publishing is also a way to preserve a consensus of ideas, facts and values. Cataloging this consensus in a public manner helps communities remember their past. It extends that in-person dialectic into the future so that distant communities can build on and refute the claims that came before.
Unlike flashy self-publishing platforms like Twitter and Facebook, The Bitcoin Mint Press doesn't host or need a platform to deliver a frictionless user experience. It doesn't beg strangers to feed it their interests and desires. Yet its immutable inscription to the Bitcoin ledger ensures that no one can censor it from the public’s eye.
EXCHANGING AID AND ART
Lastly, this meet-up offers more than just conversation. It allows people to exchange physical bitcoin for aid and allows creatives to share their artistic expressions of bitcoin.
These expressions are like those augmented reality QR codes you see at modern art exhibits. But instead of transporting your attention toward art transposed through digital space, they transport it to the material world. This signpost, or physical bitcoin receipt if you will, signals two things to people whose focus and presence occupy digital space. First, it signals you must leave digital space to see and experience the art. Second, it signals that you can actualize your bitcoin into new and creative expressions of art.
Now, you might be thinking, “How does physical bitcoin art differ from posting pictures of physical art on social media?” The key difference is the message and verifiability. When you post a picture of physical art, you say, "Look at what I created or discovered." You give the network a digital substitute for the real thing so people don't have to spend the energy to see the art themselves. It doesn't matter if the image is fake or if you were there because you are giving them the experience in and of the post. A physical bitcoin receipt doesn't deliver a substitute for the real thing. It invites you to experience the art in person. It's more like a classifieds posting in the newspaper. Only the posting is permanent and independently verifiable.
This public permanence allows artists to ascribe provenance and create dynamic art collections by including additional data in the minting transaction. This information, like the minting standard itself, can be recorded on the right side of the ledger—next to its corresponding transaction. There are quick and easy ways to embed this information. Simply look up "how to inscribe Ordinal collections," and you will find creative ways to string physical mints together under your authorship.
Of course, there are still ways for people to exploit this standard to funnel attention back to the machine. But as an anarchist, I'm not here to tell people what they shouldn't do with The Bitcoin Mint. I'm only here to offer an alternative approach. But if you are interested in subverting the technocratic system pervading our day-to-day, consider adopting a simple ethic.
Don't engage the matrix with fear or avoidance. Instead, approach it with courage and intention. Look for opportunities to post, coordinate physical cooperation and ghost. And if you are an artist who wants to adopt these principles, consider using the posting (see linkt.ree) for this guide as a template: [{Share inscription} {opportunity for in-person collab or exchange} {#thebitcoinmint(location)}].
This standard shows the Luddites and anarchists of the world a way to engage people within the machine on their terms—a way that doesn't feed its digital attention-harvesting objectives. Every inscription attracts local cooperation and local experience, and every local interaction it facilitates inspires more expressions of physical bitcoin art and exchange. But this propensity for growth doesn't mean that the standard needs a network effect to work. It only requires the person before you to see its unalterable ascribed definition on Bitcoin's public ledger.
The physical bitcoin attached to the physical editions of guide is part of a social experiment in mutual aid and self-determination. But I won't mince my words here. Your personal agency and orientation to the physical world is an affront to the machine. It and the people most committed to its network objectives will look for ways to stop you, pull you back in and restrain you. But you don’t need their or anyone’s permission to be free. You only need to remember the power and gift of agency this life has given you.
See the Link Tree Directory below for information and updates on the local Bitcoin Mint meet-up. And if you don't live close, share this guide and create your own space for mutual aid. Feel free to contact me directly if you have questions or want paper copies with physical bitcoin attached.
TheLosAngelesBitcoinMint #TheBitcoinMint
-
 @ 0461fcbe:35a474dd
2025-03-13 23:10:12
@ 0461fcbe:35a474dd
2025-03-13 23:10:12Background
I will start with a disclaimer: I'm all-in on Nostr. But before that, I spent 4 years building on ActivityPub. Then in Feb 2023 I built a bridge between ActivityPub and Nostr, and in Dec 2024 I built another bridge between Nostr and Bluesky. Most of all I am committed to open source and the decentralized vision. Having experience with all 3 major protocols, I still think Nostr is the best, but Bluesky outshines it in some major areas. The main reason for this blog is to explore the things Bluesky does better than us, and to point out why I still think Nostr is the best solution.
This is a technical blog. For a more high level overview of decentralized protocols, see: https://soapbox.pub/blog/comparing-protocols/
Data Model
Nostr and Bluesky both allow users to store any type of data in a single, unified format. Nostr calls them events. Bluesky calls them records. They are mostly interchangeable ideas, but the way the data is stored and retrieved is very different.
It's worth noting that, like Nostr and ActivityPub, Bluesky is capable of doing anything under the sun. It's a misconception that it can't. You can build whatever Reddit, TikTok, or other stuff clone on Bluesky just fine. It's limited more by the huge knowledge gap you have to overcome than it is by anything about its data model.
NSIDs vs Kinds
Nostr events use a "kind" number, eg
1, to distinguish different type of events. Bluesky records use what they call an "NSID" (namespace identifier), egapp.bsky.feed.post, which is a reverse-DNS string notation.Nostr's
"kind": 1is equivalent to Bluesky's"$type": app.bsky.feed.post.I think Bluesky's system is better, because it allows developers to feel like what they built is "real" without having to get it merged into the NIPs repo, which is basically like an IANA of Nostr kind numbers. I believe this causes significant problems on Nostr, and makes people feel like they are being held back by others. That being said, the counter-argument is that kind numbers encourage interoperability for the very same reasons. The barriers to adding new kinds pushes people to work with what's already there.
Text Content Formatting
Kind 1 events ("plain text notes", ie "Tweets") on Nostr have developed in a haphazard way over time, by many people piling things onto it without taking a step back to assess a unified way to handle it. Some examples include:
- NIP-21
nostr:URIs imetatags- inline media embeds as URLs without
imetatags - unspec'd Markdown rendering by some clients
- legacy specs such as positional mentions (eg,
#[0], mostly gone now)
What we have now is quite a mess, and it's something Bluesky beats us on badly.
Bluesky has a plaintext content field that can be displayed as-is. In addition, it has a "facets" field, which is a structured JSON object, that adds rich-text information such as formatting (bold, italic, etc), links, mentions of users, and whatever else metadata about the text.
This is an extensible system that beats even options like Markdown, due to its ability to include native extension like mentions, and its ability to be parsed by any programming language or software environment.
Bluesky is the winner here.
Syncronization
Nostr and Bluesky are both thought to be descended from Scuttlebutt, an older decentralized protocol.
On Scuttlebutt, a user's whole post history needed to be available for them to make a new post. Scuttlebutt uses a linked list, so each new event would need to reference the one before it. Only linear paths are allowed, so if a "fork" occurred (intentionally or not), only one version would be kept, and the other discarded. This lead to occasional publishing issues, but it allowed readers to assemble a complete view.
Nostr strayed from this draconian approach, removing it entirely and allowing user data to be fragmented. Meanwhile Bluesky, instead of removing it entirely, made it work more like git so that branches could be merged.
Both approaches have tradeoffs. Bluesky's approach has much higher complexity. Also, it's sometimes considered an advantage for events to be fragmented (eg Nostr allows sending DMs to specialized relays for enhanced privacy).
But Bluesky has a true account "sync" mechanism, and Nostr does not. Nostr can send filters to relays to gather events, but it cannot know when to stop looking. Proposals like Negentropy in Nostr do not solve author syncing, and only make typical relay filtering more efficient.
I think it's important to think about Nostr's "outbox" problem as a syncronization problem, and for Nostr to approach syncronization with the goal of syncronizing authors specifically.
I think Bluesky "wins" this one, if only because they have solved a problem that we haven't. Instead of copying their solution, I think Nostr should try to learn from this to recharacterize the "outbox" problem as an author syncing problem, and see if we can come up with a better solution that works for Nostr.
Knowledge Gap
One of the biggest hurdles of Bluesky, and by extension one of the greates appeals of Nostr, is in how easy it is to learn and build on.
Nostr can be understood in a couple of hours. Mastering it is difficult, but limited only by your time and imagination. Hundreds of developers are building new projects on Nostr today. Based on my experience, it seems to me that the Nostr developer community is larger than that of both ActivityPub and Bluesky combined.
Bluesky on the other hand requires a Harvard degree in Blueskyology. I believe that ameteur coders feel a sense of superiority after spending six weeks learning how to commit a post. To learn Bluesky you will have to sift through thousands of technical documents about all kinds of abstractions, especially related to IPFS and IPLD. You will have to master unnecessary technologies like CBOR (which is basically just JSON except it's in binary and takes up the same amount of space). And you will be frequently pointed to academic topics such as "DAG" and "graph theory", all just to say "it's a fucking graph". I will never understand why people will take simple concepts such as a "tree", and then make it harder to understand on purpose by saying it's more than that.
While building on Bluesky, I began to question if the creators did this on purpose. I wondered if they tried to make it complex on purpose, as a sort of IQ test and protective measure to weed out the undeireables. In my view, a truly free and open network must be accessible to all, with the hope that even non-programmers could learn how it works.
Technical complexity is not just an issue of inclusion, but also security. ActivityPub software has been found to be littered with major security holes due to its inherently complex design, while Nostr's simple design makes its attack surface extremely minimal. Bluesky has already had a few mishaps, and it makes me wonder how Bluesky will fare in the long term.
Decentralization
I will keep this short. Bluesky is designed to be decentralized, but isn't. It reminds me of the communist idea about the "withering away of the state". The idea is that you're supposed to first sieze power and become the new state, and then under your rule the state will slowly disappear because you are doing all the right communist things. I think this is basically how Bluesky sees itself (whether they agree with the analogy or not).
Nostr is decentralized, but it is a loaded gun. You're more likely to kill yourself with a gun than someone else. This is on purpose, because it wholly embraces the consequnces of being truly decentralized.
In my view Nostr gets it right. Social media has been done to death by now, so I do not think it's worth the compromise to prioritize UX over decentralization. If that's the case we have not fixed anything. It's best to start with the purist idea and work backwards to UX, rather than start with UX and work backwards to decentralization. Many people have already written extensively about the decentralization of Bluesky, so I'll leave it at that.
- NIP-21
-
 @ 57d1a264:69f1fee1
2025-03-27 08:11:33
@ 57d1a264:69f1fee1
2025-03-27 08:11:33Explore and reimagine programming interfaces beyond text (visual, tactile, spatial).
"The most dangerous thought you can have as a creative person is to think you know what you're doing."
— Richard Hamming[^1]https://www.youtube.com/watch?v=8pTEmbeENF4
For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.
'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,' explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: "We don't know what programming is. We don't know what computing is. We don't even know what a computer is." And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.'
More details at https://worrydream.com/dbx/
[^1]: Richard Hamming -- The Art of Doing Science and Engineering, p5 (pdf ebook)
originally posted at https://stacker.news/items/926493
-
 @ e5de992e:4a95ef85
2025-03-27 04:45:04
@ e5de992e:4a95ef85
2025-03-27 04:45:04Overview
On March 26, 2025, U.S. stock markets closed with notable declines driven primarily by President Donald Trump's announcement of a 25% tariff on all imported automobiles. This move has raised concerns about global trade tensions and inflation risks, impacting various sectors—especially technology and auto.
U.S. Stock Market Performance
- S&P 500:
- Dropped 1.1%
- Closed at 5,714.32
-
Broke a three-day winning streak
-
Dow Jones Industrial Average (DJIA):
- Decreased by 0.3%
-
Closed at 42,455.78
-
Nasdaq Composite:
- Fell 2%
- Finished at 17,906.45
- Led by significant losses in major tech stocks such as Nvidia and Tesla
These declines were primarily driven by the auto tariff announcement.
U.S. Futures Market
- S&P 500 Futures:
-
Remained flat, indicating investor caution amid ongoing tariff uncertainties
-
Dow Jones Futures:
- Showed little change, reflecting a wait-and-see approach from market participants
Note: U.S. futures are exhibiting minimal movement with low volume.
Key Factors Influencing U.S. Markets
Auto Import Tariffs
- President Trump's imposition of a 25% tariff on imported automobiles has heightened concerns about escalating trade wars.
- Major automakers, including General Motors and Ford, experienced stock declines in response to these tariffs.
Tech Sector Weakness
- Leading technology companies, notably Nvidia and Tesla, saw significant stock price reductions (each dropping more than 5%), contributing to the overall market downturn.
Energy Sector Performance
- Despite a 4% fall in oil prices, energy stocks outperformed the broader market by rising 8.9% compared to a 1.8% decline in the S&P 500.
- However, the energy rally appears fragile, driven by increased valuations rather than improving earnings prospects.
Global Stock Indices Performance
- Japan's Nikkei 225:
-
Declined by 1.2%, with major automakers like Toyota experiencing significant losses due to tariff concerns.
-
South Korea's KOSPI:
-
Fell 0.7%, impacted by declines in auto-related stocks amid trade tension fears.
-
Hong Kong's Hang Seng:
-
Dropped 2.35%, closing at 23,344.25, influenced by a downturn in Chinese tech shares and ongoing tariff concerns.
-
Germany's DAX:
-
Experienced a slight decline of 0.32%, closing at 23,109.79, as initial optimism regarding tariff negotiations waned.
-
UK's FTSE 100:
- Fell marginally by 0.10%, reflecting investor caution amid mixed economic data.
Cryptocurrency Market
- Bitcoin (BTC):
-
Trading at approximately $88,500, reflecting a 1.5% increase from the previous close.
-
Ethereum (ETH):
- Priced around $2,100, marking a 1.2% uptick from the prior session.
These movements suggest that investors may be turning to digital assets as alternative investments during periods of traditional market uncertainty.
Key Global Economic and Geopolitical Events
- Trade Policy Developments:
- President Trump's new auto tariffs have intensified global trade tensions.
-
Concerns include retaliatory measures from trading partners (e.g., Japan and Canada) and potential disruptions to international supply chains.
-
Energy Sector Outlook:
-
Despite recent gains, the energy rally appears fragile as it is driven more by increased valuations than by improving earnings.
-
Market Forecasts:
- Barclays has lowered its year-end price target for the S&P 500 to 5,900 from 6,600, citing concerns over the tariffs’ impact on earnings. This is the lowest target among major U.S. Treasury dealers, reflecting growing apprehension about the economic outlook.
Conclusion
Global financial markets are navigating a complex landscape marked by escalating trade tensions, sector-specific challenges, and evolving economic forecasts. Investors are advised to exercise caution and closely monitor these developments—particularly the impact of new tariffs and their ripple effects on global trade and inflation—when making informed decisions.
-
 @ 04c915da:3dfbecc9
2025-03-13 19:39:28
@ 04c915da:3dfbecc9
2025-03-13 19:39:28In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ a8d1560d:3fec7a08
2025-03-27 03:12:03
@ a8d1560d:3fec7a08
2025-03-27 03:12:03I have made a big update to my Nostr desktop. Apps for images, videos and livestreams after their respective NIPs have been added, and the Raw Events app has been greatly improved. There are still some layout problems, but it all works (hopefully).
https://websim.ai/@wholewish91244492/nostr-desktop
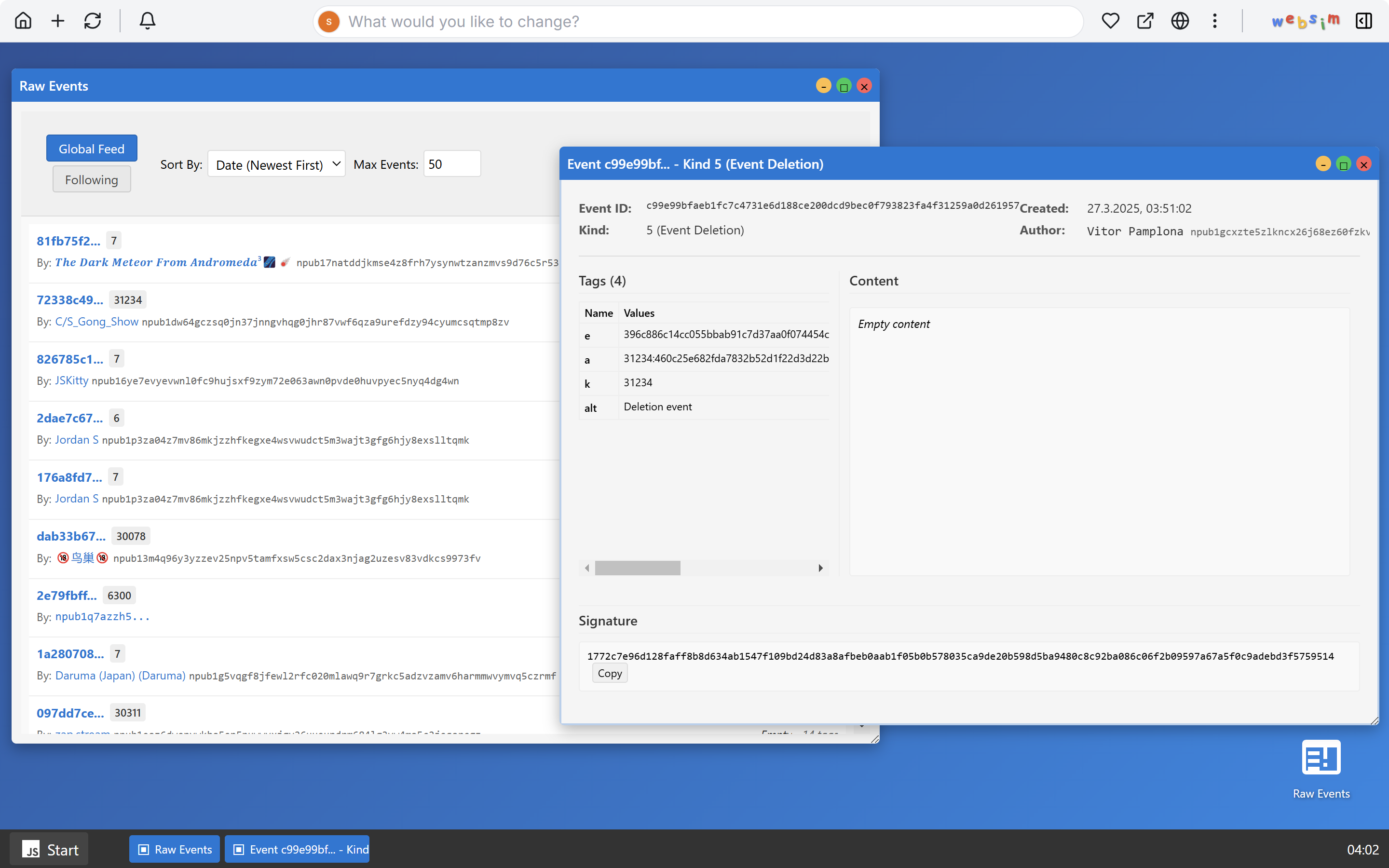
-
 @ 9f475ec5:d9acc946
2025-03-26 23:18:41
@ 9f475ec5:d9acc946
2025-03-26 23:18:41The next step in AI evolution is enabling AI agents to communicate directly with one another.
"Agents on Nostr, combined with cashu, would be amazing" — Jack Dorsey, Citadel Dispatch #150
Today
For AI agents to communicate seamlessly, they need a universal language that allows frictionless data and instruction sharing—one that surpasses the constraints of isolated systems. Just as humans rely on shared languages to collaborate, AI agents require a common “dialect” to exchange information, delegate tasks, and build collective intelligence. Without it, each agent’s logic remains siloed, limiting synergy and innovation. A universal protocol, however, lets agents seamlessly tap into one another’s capabilities, coordinating strategies, sharing learned knowledge, and multiplying their creative potential. By aligning on an open, interoperable standard, AI can flourish into a vibrant, interconnected ecosystem rather than a patchwork of stand-alone solutions. This is no different from what happened with the Internet when HTTP was released, leading to the development of web browsers and the Internet as we know it today.
Nostr can be viewed as the “HTTP” for agent-to-agent communication—both are open standards that encourage universal participation and spark rapid innovation. When Tim Berners-Lee released HTTP without proprietary restrictions, developers everywhere could build websites and online services on a simple yet extensible protocol. In the same way, Nostr’s minimalistic yet powerful design fosters a decentralized, censorship-resistant foundation for diverse messaging, social, and identity systems. Just as HTTP created an open arena for web platforms and APIs, Nostr offers a flexible, community-driven substrate for agent-based communication, promoting a spirit of collaboration and interoperability crucial to long-term growth.
Our vision
We envision a world where AI agents operate on an open, standardized, and decentralized network —a Nostr agentic ecosystem that unlocks new levels of creativity and collaboration.
Our mission is to develop the tools and infrastructure that enable AI agents to seamlessly interoperate over the Nostr network—facilitating the exchange of both data and money.
Our first steps
Every marketplace application faces the chicken and egg problem. Sellers won't show up until the buyers are there and buyers won't show up until the sellers are there.
Our solution? The FIFA 2026 World Cup will bring millions of international and domestic travelers to 11 cities in the US.
Can we work with chambers and tourism agencies around these cities to embbed Nostr powered AI travel organizers into their websites and apps? This could be a way to onboard thousands of businesses to the Nostr agentic ecosystem. This is our growth assumption.
That's why our our first step is to provide businesses—large and small—with a turnkey platform to sell their products and services to any AI agent connected to the open Nostr network.
We will also develop the tools for websites and apps to develop Nostr-powered AI buyers and, with the support of the local chambers and tourism boards, direct their technology suppliers to use these tools.
Our values
Everything we develop is free and open sourced under the MIT license and our business will generate revenue by charging a monthly fee for operating an end-to-end agentic commerce solution to the businesses selling their products through the Nostr agentic ecosystem.
A rough demo
Today, we is just nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m 😁 I've created a proof-of-concept buyer AI agent and published real information from some merchants to demonstrate the concept to local chambers and validate the growth assumption.
Feel free to check it out at the Synvya agentstr repository, but be warned, I'm not a programmer so don't freak out with the code.
You can also see a demo here:
nostr:naddr1qvzqqqy9hvpzp868tmzceg2pvymlpdssv8shvu2jlndysp6dxwc67gw5jtv6ej2xqq2hgnfnwdf8yendfa8r2jttdsck6dm0wpm4wnalksn
Interested?
If this sounds interesting to you, follow nostr:npub1nar4a3vv59qkzdlskcgxrctkw9f0ekjgqaxn8vd0y82f9kdve9rqwjcurn or nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m and reach out at any time.
-
 @ 19220736:7578e0e9
2025-03-13 13:42:58
@ 19220736:7578e0e9
2025-03-13 13:42:58On January 29, 2025, President Donald Trump issued a new executive order reinforcing and expanding the measures introduced in his 2019 Executive Order 13899, titled "Combating Anti-Semitism." The original order aimed to address rising anti-Semitic incidents, particularly in educational institutions, by directing federal agencies enforcing Title VI of the Civil Rights Act of 1964 to consider the International Holocaust Remembrance Alliance's (IHRA) definition of anti-Semitism when evaluating discrimination complaints. This definition includes certain criticisms of Israel as potential examples of anti-Semitism.
While intended to protect Jewish students from harassment based on shared ancestry or ethnic characteristics, it also raised concerns about potential restrictions on free speech, particularly regarding criticism of Israel. The new 2025 order intensifies these efforts, mandating federal agencies to use all available legal tools to prosecute individuals involved in antisemitic harassment and violence. Additionally, it directs educational institutions to monitor and report foreign students and staff activities, further broadening the scope of federal oversight in academic settings that may violate grounds of inadmissibility under U.S. law.
Targeting non-citizen participants, the order mandates the deportation of foreign nationals involved in pro-Palestinian protests on U.S. university campuses, citing concerns over antisemitism. This move has raised significant concerns regarding free speech, as it appears to target students and activists who engaged in pro-Palestinian protests on U.S. university campuses during the Israeli response after the Hamas attack on October 7, 2024. Critics argue that the executive order will suppress constitutionally protected speech and compel universities to monitor student activities.
As a response to President Trump’s executive orders prohibiting antisemitism, U.S. Immigration and Customs Enforcement arrested Mahmoud Khalil, a Palestinian graduate student and U.S. permanent resident, at his Columbia University residence on March 9, 2025. Authorities allege his involvement in activities aligned with Hamas, though he hasn't been charged with any crime. His lawyer, Amy Greer, criticized the detention as politically motivated. This arrest follows the Trump administration's revocation of Khalil's green card and threatens to withdraw $400 million in federal funding from Columbia University over alleged antisemitic harassment on campus.
The arrest of Mahmoud Khalil stands as a reminder that when the state starts wielding immigration law and funding as a weapon against dissent, no voice is safe. Under the guise of combating antisemitism, this executive order threatens to trample the First Amendment, blurring the line between hate speech and legitimate protest. If criticizing a foreign government's policies can now trigger deportation, then the dance of free speech is over, replaced by a march of silence. And that is a danger we cannot ignore.
-
 @ 22050dd3:480c11ea
2025-03-12 20:20:50
@ 22050dd3:480c11ea
2025-03-12 20:20:50Bitcoin fixes this – what I thought immediately upon stepping off the ferry in Isla Mujeres.
An hour prior, a friend of a friend brought me to the ferry in Cancun as a private transport and I now had to transfer them money.
The backstory of why I was paying an hour after the fact doesn’t matter now. What mattered then was that I needed to find an ATM to withdraw cash. Furthermore, I also needed to find an OXO convenience store to send the cash to the friend’s bank account. If only they accepted bitcoin!
While this was my technically 2nd time in Isla Mujeres, it was 1st true time there. My technical 1st visit was when I was 9 years old with my family in 2004. Now at 30 years old and traveling solo and staying on the island for 2 weeks, this was my true first time on the island.
 ### How I Ended Up in Isla Mujeres
### How I Ended Up in Isla MujeresI had first heard about BTC Isla a few months prior in October 2024. I stumbled upon a girl named Isa on Nostr who is trying to orange-pill the island and create a Bitcoin circular economy. Subsequently, hearing her interview on Efrat Fenigson’s podcast “You’re The Voice” inspired me to reach out to Isa.
I messaged her on Nostr saying that I thought what she was doing with BTC Isla was cool and inspiring, and that I wanted to help. Flash-forward to January 13 2025 and there I was on the island with boots on the ground.
First Day
While I didn’t meet Isa until the following day during one of two Bitcoin meetups I was on the island for, my first experience with Bitcoin was later that first evening. A fellow bitcoiner on the island messaged me seeing if I wanted to grab tacos for dinner and explore the island, and that’s what we did.
However, with a severe itch to start spending bitcoin as soon as possible, I set off to the Mayakita restaurant to grab lunch and pay in bitcoin.
 Delicious food with a view!
Delicious food with a view!Mayakita is the unofficial hub for BTC Isla and is the usual meeting spot for both the Bitcoin meetups and classes. It’s in a great location with a beautiful view right on the ocean and serves up delicious food. Pair all of that with the fact that they excitedly accept bitcoin, and you’ve got a restaurant that I’d frequent almost every day during my 2 weeks on the island.
Later that evening, the fellow bitcoiner picked me up and we went out for a taco dinner. Naturally, we paid for the tacos with bitcoin, and it was an exciting experience!
The owner of the restaurant was glad to accept bitcoin and chatted with us a little. He seemed intrigued to hear that I had traveled from the US to Isla Mujeres specifically because of Bitcoin.
Later that evening, while exploring the island, we stopped by a food cart serving churros that had recently started accepting bitcoin. I was finally able to have some delicious churros again after being away from Mexico for a year, and best of all was able to pay for them with bitcoin.
 Octopus tacos!
Octopus tacos!There was a visible reaction and excitement from the cart owners when they saw us pull up. They knew my friend, and knew that our arrival meant they’d get to stack some sats and receive some bitcoin!
It was a solid first day on the island. I reunited with the Mexican food that I love dearly and also paid for it all with bitcoin. Wins all around!
Day 2: Bitcoin Meetup & Down To Business
The next day was a big one, as first there was a Bitcoin meetup in the morning! Afterwards, Isa and I would be spending the afternoon together working on BTC Isla and driving around orange-pilling merchants.
I found the meetup especially fun because it was only the second Bitcoin meetup I had ever attended.
The friend from the previous evening’s adventures was there, as well as several others. Breakfast, coffee, and smoothies were enjoyed by everyone and paid for in bitcoin.
The official BTC Isla tuk-tuk also made an appearance!
 Isa brought it out to the front of the restaurant for the meetup. As is a new tradition for BTC Isla, the new Bitcoiners to the island signed the tuk-tuk and posed for a picture with it. A fun tradition and a way to display community growth, in my opinion.
Isa brought it out to the front of the restaurant for the meetup. As is a new tradition for BTC Isla, the new Bitcoiners to the island signed the tuk-tuk and posed for a picture with it. A fun tradition and a way to display community growth, in my opinion.After the meetup, Isa and I got to work discussing ways I could help her with BTC Isla during my 2 weeks on the island. We then set off in a golf cart to start visiting merchants and try to orange-pill.
In total, we went to about 10-12 places that afternoon, officially orange-pilling one merchant!
 We handed out a flyer I had made to several other businesses and had a few conversations with owners as well. Some businesses were completely uninterested in Bitcoin, not even wanting to hear what we had to say. Others, however, were intrigued and were happy to chat.
We handed out a flyer I had made to several other businesses and had a few conversations with owners as well. Some businesses were completely uninterested in Bitcoin, not even wanting to hear what we had to say. Others, however, were intrigued and were happy to chat.While we only got one new merchant to accept bitcoin, we felt good about our efforts. We likewise felt confident that 2 or 3 businesses would start accepting bitcoin after thinking it over.
My lack of Spanish-speaking ability was frustrating for me. It was clear that it would be an obstacle in my goal to orange-pill 10 merchants while on the island.
My first 2 days on the island were a smashing success in my mind. Now, I had some goals and tasks to work on over the next 10 days, and I was eager to start.
-
 @ 878dff7c:037d18bc
2025-03-26 21:55:34
@ 878dff7c:037d18bc
2025-03-26 21:55:34Popular Grocery Items Recalled Due to E. coli Contamination
Summary:
Several Fresh Salad Co products sold in Queensland and northern New South Wales have been recalled due to contamination with Shiga toxin-producing E. coli (STEC). Affected items include baby spinach (120g, 280g), baby spinach and rocket (120g), and a stir-fry mix (400g) with specific use-by dates at the end of March. Consumers are advised to return these products for a full refund and seek medical advice if concerned about their health.
Sources: News.com.au - March 27, 2025
Coalition Proposes Halving Fuel Excise to Alleviate Cost of Living
Summary:
Opposition Leader Peter Dutton has announced that, if elected, the Coalition would repeal Labor's planned tax cuts and instead implement a 12-month halving of the fuel excise. This initiative aims to reduce petrol prices by 25 cents per litre, providing immediate relief to Australian families and workers facing cost-of-living pressures. The proposal contrasts with Labor's tax cuts, which are set to commence in 15 months and offer annual savings of up to $536 for taxpayers.
Sources: The Guardian - March 27, 2025, The Australian - March 27, 2025
Federal Budget Criticized for Omitting Key Infrastructure Funding
Summary:
Groom MP Garth Hamilton has criticized the latest federal budget for lacking funding for critical infrastructure projects in his region. He expressed concerns over the future of regional programs like the Growing Regions and Regional Precincts and Partnerships Programs, which he believes are essential for regional development. Hamilton highlighted the absence of funding for key projects such as the New England Highway, the deteriorating Warrego and Gore Highways, and the stalled Inland Rail project.
Source: The Courier-Mail - March 27, 2025
China Faces Challenges in Advanced Robotics Development
Summary:
China is recognizing the importance of robots in its ageing economy, facing a significant labor shortage. Despite leading in industrial robot installations, most Chinese robots are low-tech compared to advanced humanoids being developed elsewhere. The U.S. and China are both racing to develop sophisticated robots, but China's sector remains reliant on foreign components and faces potential limitations from U.S. sanctions. This dependency makes China's position in the robotics race precarious.
Sources: Reuters - March 26, 2025
Tax Cuts Passed Amid Election Speculation
Summary:
Labor's budget tax cuts have been swiftly passed into law, providing the average worker with modest financial relief starting next year. This development leaves Opposition Leader Peter Dutton with a strategic decision on how to position the Coalition's response in the lead-up to the federal election. Sources: 9News - March 27, 2025
Labor Government Proposes Tax on Unrealized Superannuation Gains
Summary:
The Labor government has introduced a proposal to levy a 15% tax on unrealized capital gains for superannuation balances exceeding $3 million. This initiative aims to generate an additional $9.7 billion between 2024-25 and 2028-29. Critics argue that taxing unrealized gains is unfair and may discourage investment, while supporters contend it promotes fairness in the superannuation system. Sources: News.com.au - 27 March 2025
New Youth Crime Bill Introduced in NSW Parliament
Summary:
The State Opposition Attorney General, Alister Henskens, is set to introduce the Crimes Legislation Amendment (Youth Crime) Bill 2025 to the NSW Parliament. The bill aims to combat youth crime by expanding the definition of repeat offenses, revoking bail under specific conditions, and implementing electronic monitoring and mandatory curfews for repeat offenders. The proposal has sparked debates regarding its potential impact on regional communities and the principle of doli incapax. Sources: The Daily Telegraph - 27 March 2025
Prime Minister Albanese Invites President Trump to Visit Australia Amid Tariff Dispute
Summary:
Prime Minister Anthony Albanese has revealed plans to visit Washington D.C. if he wins the upcoming May election, marking his first international trip. This follows the U.S. imposition of 25% tariffs on steel and aluminum imports from Australia. Despite the tariff dispute, Albanese has invited President Donald Trump to visit Australia, which would be his first trip to the country as President. The timing of Trump's visit would depend on his schedule. Both major Australian political parties remain committed to seeking a solution to the steel and aluminum levies through persistent engagement with the U.S., rejecting reciprocal tariffs on U.S. imports. Sources: News.com.au - March 26, 2025
Jewish Groups Criticize Australia's Continued Funding to UNRWA
Summary:
Jewish groups have criticized the Australian government's decision to continue funding the UN Relief and Works Agency for Palestine Refugees (UNRWA), amounting to $20 million. Concerns have been raised about UNRWA's past associations with terrorism, with claims that its employees participated in the atrocities of October 7. The Executive Council of Australian Jewry has called for the withdrawal of funding, labeling the organization as compromised. Despite this opposition, the Australian government has defended its financial support for humanitarian purposes, ensuring stringent controls and safeguards. This issue adds tension to the upcoming election, reflecting concerns within Jewish and Muslim communities. Sources: The Australian - March 26, 2025
Australia's Inflation Rate Decreases, Offering Relief to Mortgage Holders
Summary:
Australia's annual inflation rate has fallen to 2.4% as of February, down from the previous month's 2.5%. This decline is attributed to eased rental prices, reduced new home costs, and falling electricity prices due to government rebates. The Reserve Bank of Australia's preferred measure, the "trimmed mean," also decreased to 2.7%. This trend is promising for mortgage holders anticipating potential interest rate cuts and for the Labor government focusing on cost-of-living issues ahead of the upcoming election. Sources: The Guardian - March 26, 2025, Reuters - March 26, 2025
Queensland Farmer Revolutionizes Cattle Mustering with Drones
Summary:
Luke Chaplin, a fourth-generation grazier from northwest Queensland, has transformed cattle mustering by utilizing drones through his company, SkyKelpie. This innovation has managed over 300,000 livestock across Australia efficiently and cost-effectively. Supported by the Queensland Government and Meat & Livestock Australia, the drone technology offers a high return on investment compared to traditional methods, reducing animal stress and improving herd management. SkyKelpie is also developing online training courses and collaborating on autonomous mustering technologies using AI and image detection. Sources: The Courier-Mail - March 27, 2025
Anduril Sees Positive Outlook with New U.S. Defense Policies
Summary:
Anduril President Christian Brose expressed optimism about the company's prospects under the new Trump Pentagon administration, which is perceived to be more receptive to autonomous defense systems. Anduril plans to partner with OpenAI to enhance national security missions and is expanding its manufacturing capabilities, including potential international expansion in Australia. The company develops autonomous systems like the Ghost Shark, offering rapid deployment and cost efficiency compared to traditional manned military assets. Source: Reuters - 27 March 2025
Controversial Legislation Passed to Protect Tasmanian Salmon Industry Amid Environmental Concerns
Summary:
The Australian Parliament has passed a contentious bill aimed at safeguarding Tasmania's salmon farming industry, specifically in Macquarie Harbour. This legislation limits the federal environment minister's authority to review long-standing projects, effectively halting an ongoing assessment of the 2012 expansion of fish farming in the area. Critics argue that this move compromises environmental standards and threatens the endangered Maugean skate. Notably, Greens Senator Sarah Hanson-Young protested by displaying a dead salmon in the Senate chamber, and international figures like Leonardo DiCaprio have called for the shutdown of destructive salmon farms to protect marine life. The government maintains that the law addresses specific regulatory issues and won't affect new projects related to coal, gas, or land-clearing. Sources: The Guardian - March 27, 2025, Herald Sun - March 27, 2025, News.com.au - March 27, 2025, The Australian - March 27, 2025
The 5 Types of Wealth – Real Talk with Zuby ft. Sahil Bloom (Episode #349)
Summary:
In this insightful episode of Real Talk with Zuby, entrepreneur and writer Sahil Bloom joins the show to break down his popular framework of "The 5 Types of Wealth." The conversation goes beyond money, exploring what it truly means to live a rich and fulfilling life.
Bloom outlines the following five categories of wealth:
- Financial Wealth – Income, savings, investments – the traditional definition of wealth.
- Social Wealth – Relationships, reputation, network, and community impact.
- Physical Wealth – Health, fitness, energy levels, and lifestyle habits.
- Mental Wealth – Emotional resilience, knowledge, creativity, and mindset.
- Time Wealth – Freedom and control over how you spend your days.
Key Highlights & Insights:
- Reframing Success: Bloom critiques the modern obsession with financial success and emphasizes that true prosperity is multidimensional.
- Balance vs. Optimization: He talks about how chasing one form of wealth (e.g., money) at the expense of others often leads to long-term regret.
- Time as the Ultimate Currency: The discussion touches on the importance of buying back your time and designing a life where you're not constantly reacting.
- Health & Longevity: Physical wealth is highlighted as the foundation that enables enjoyment of the other four.
- Practical Framework: The episode includes a useful breakdown of how listeners can audit and improve each area of wealth in their own lives.
This episode offers a thought-provoking lens for anyone reassessing their priorities or striving for more balanced success.
Source: Spotify - 27 March 2025