-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ 554ab6fe:c6cbc27e
2025-04-10 18:48:57
@ 554ab6fe:c6cbc27e
2025-04-10 18:48:57What is consciousness, and can it be changed or enhanced? This is a question that humans have struggled with for a very long time. The question of consciousness alone is daunting. Some even argue that humans will never be able to find the answer. Regardless, the quest for knowledge is not always about the answer, rather it is the journey that is revealing. This is true not only for our society, but the individual as well. The search for the truth often leads one down a path of self-reflection, and can lead to conclusions previously thought to be ludicrous. Here, I will argue that consciousness can be interpreted as an interpretation of reality, where the interpretation may become clearer and more accurate through practices such as meditation.
Consciousness
To articulate this idea, the concept of consciousness must firstly be discussed. There is an incredibly interesting TED talk given by Anil Seth, where he describes consciousness as an illusion. He explains how the brain receives signals from both the internal and external environment of the body, makes an interpretation of those signals, which creates our conscious experience. In his scientific writing, he claims that the brain can be viewed as a prediction machine1. He argues that the brain is constantly making predictions and error correcting in order to gain understanding of the signals it is receiving. He is not alone in this theory, and many other researchers concur that the constant comparison of internal predictions and external stimuli is what generates the brain’s sensations of causal forces2. There are plenty of reasons to believe this is true. Imagine, the brain is receiving all kinds of neuronal signals both from external stimuli sensors and sensors for our internal systems. These signals all shoot up the spinal cord to the brain. It is unclear that these neuronal signals are stamped with an identifier of where they came from, so the brain has to make a predictive model for not only where the signal came from, but also why the signal came at all. The latter is important for survival: the use of our senses to accurately predict our environment would be a critical reason why consciousness developed in the first place. Imagine you are an ancient hominid walking in the wild: you see a tangled cord like thing around a branch on the tree. You need to process that information, determine if it is more branch or a snake and act accordingly. This is a potential biological reason for the manifestation of thought and problem solving. This is a very meta-cognitive example of our brain receiving information and then using previous knowledge to generate a predictive conclusion on the external reality.
There are also examples of this outside of the more obvious meta-cognitive examples. A good example is the famous rubber hand experiment. The first rubber hand experiment was conducted in 1998 by Botvinick and Cohen3. In this experiment, a subject places their hand on a table with a screen blocking their view of their own hand. A rubber hand is then placed on the other side of the screen where it is visible. The experimenter rubs both the rubber hand and real hand with a paint brush. By the end of the experiment, subjects begin to feel as if the rubber hand is their own limb3. The brain, using the visual senses, detects that a hand is being stroked with a brush while sensory neurons send signals that the hand is experiencing the touch of a paint brush. These two signals cause the predicting brain to think that the rubber hand is our hand. This experiment has been repeated many times in different ways. It has been observed that participants begin to react defensively to the threat of pain or damage to the rubber hand4. This illustrates the powerful extent at which the brain processes and reacts to information that it interprets from reality. Amazingly, some research suggests that the touch aspect of the experiment isn’t even necessary to produce the illusion5. Others have recreated this experience using virtual reality, citing that when the virtual hand changed color in response to the subject’s heartbeat, a significant sense of body ownership was generated6. Body ownership, and our sense of reality is arguably determined by our brain’s interpretation of both internal and external stimuli.
The Neuroscience and Meditation
It is hypothesized that the anterior insular cortex (AIC) is involved in the comparison of the stimuli to the predicted model1. Interestingly, the same brain region is associated with the anticipation of pain7. For those unaware, there is some research to suggest that much of the pain we experience is not due to the actual noxious stimuli (physical pain sensation), but from the anticipation of that pain. Evidence for this can be found in studies such as Al-Obaidi et al. from 2005, that concluded that the pain experienced in patients with chronic low back pain could not be solely attributed to the sensor signals, but from the anticipation of the pain8. Additionally, the anticipation of pain relief is the primary contributor to placebo analgesia (placebo pain killers)9. Furthermore, a large body of research has been conducted showing that meditators show a decreased anticipatory attitude towards pain, subsequently experiencing less unpleasant pain 7,10,11. For example, chronic pain in multiple areas such as the low back, neck, shoulder, and arms have been shown to reduce after meditation practice12. Finally, an extreme case study worth noting is of a yogi master who claimed to not experience pain at all13. When this master was brought into the lab, not only did he not experience pain, but his thalamus showed no additional activation following painful stimuli13. What is fascinating about this is that the thalamus is the main relay station for all incoming somatosensory information14, and some argue that this is a candidate for the location of consciousness15. To not have strong activation here after painful stimuli is to suggest a radical change in how the brain receives incoming stimuli, and perhaps is indicative in a dramatic shift in how this individual’s conscious experiences the world. Though this is but one small example, the previous studies outline a strong case for meditation’s ability to alter the way the brain processes information. Given meditation involves the active practice of generating an open and non-judgmental attitude towards all incoming stimuli, perhaps this alters the processing of incoming stimuli, thereby changing the predictive model. On a similar note, perhaps it relates to neuroplastic changes that occur within the brain. It has been noted that the AIC is activated during times of awareness of mind wandering16. This suggests that the AIC is in use frequently during meditation practices. Perhaps it is strengthened then by meditation, thereby also allowing for greater prediction model generation. Imagine the mind as a pond. If the pond is calm and still, one single rain drop rippling in the pond is clearly identifiable. One would easily know information about the droplet, because the ripple could be easily analyzed. Now imagine a pond during a rain storm, where an uncountable amount of rain drops is hitting the pond and there are ripples everywhere. One could not adequately make out where each ripple came from, because there would be too much overlap in the ripples. This may be how the brain functions as well. When the signals are low, and no extraneous thoughts and interpretations are created from signals, then the brain’s prediction model can easily determine where and why a signal it received came from. If, however, the mind is chaotic and full of internal noise, then the brain has a harder time creating an accurate understanding of incoming stimuli and generating a correct model.
Enlightenment
Enlightenment, from a scientific point of view, has been defined as a form of awareness where a person feels that s/he has gained a new understanding of reality 17. In this sense, it bears a striking relationship to the topic of consciousness. If consciousness can be defined as our interpretation of the external and internal environment through our mental prediction model, then experiences of enlightenment are defined by moments where our interpretation is completely changed in a profound way. The experiences are often characterized by the loss of individuality and consequent identification of being part of a greater oneness 18,19. As an interesting side note, this same experience is common amongst subjects, who in a double-blinded study, take psilocybin (the active ingredient in magic mushrooms)20,21. The neuroscience of enlightenment is particularly interesting. The temporo-parietal junction of the brain is involved with self-location and body ownership22. Unsurprisingly, this area is highly involved in the illusion of the rubber hand experiment23. This is the same brain area that is hypothesized to be related to these enlightened experiences of oneness 17. If this brain area, which handles the interpretation of where and what the body is, was to decrease in activation, then the brain would generate a more ambiguous interpretation that the self and the external environment are less distinct than previously thought. This is a possible explanation to why enlightenment experiences involve a feeling of oneness with everything. To bring this all home, meditation has been shown to decrease parietal lobe activation 4,24. Suggesting that meditation can be a method of adjusting the brain’s interpretation of stimuli to generate an outlook that is unifying in perceptive.
Closing Remarks
The evidence that meditation may lead to an altered conscious living has deep philosophical implications. Meditation is a practice that, in part, involves an open awareness to all incoming stimuli alongside the absence of any meta-cognitive interpretation or processing of said stimuli. This generation of a still mind may generate a more accurate prediction model of incoming stimuli, void of any corruption on the part of our thoughts. Given the observation that meditation, both scientifically and culturally, can lead to an understanding and experience of a greater oneness amongst all suggests that this interpretation of incoming stimuli is the more accurate interpretation. It is hard to imagine that anyone would not advocate the beauty and usefulness of this perspective. If more people had this perspective, we would have a much more peaceful, happy and unified society and planet. Ironically, our culture often aims to arrive to this philosophical perspective through analytical thought. However, given the evidence in this post, perhaps it is the absence of analytical thought, and the stillness of the mind that truly grants this perspective.
**References ** 1. Seth AK. Interoceptive inference, emotion, and the embodied self. Trends in Cognitive Sciences. 2013;17(11):565-573. doi:10.1016/j.tics.2013.09.007 2. Synofzik M, Thier P, Leube DT, Schlotterbeck P, Lindner A. Misattributions of agency in schizophrenia are based on imprecise predictions about the sensory consequences of one’s actions. Brain. 2010;133(1):262-271. doi:10.1093/brain/awp291 3. Botvinick M, Cohen JD. Rubber hand ‘feels’ what eyes see. Nature. 1998;391(February):756. 4. Newberg A, Alavi A, Baime M, Pourdehnad M, Santanna J, D’Aquili E. The measurement of regional cerebral blood flow during the complex cognitive task of meditation: A preliminary SPECT study. Psychiatry Research - Neuroimaging. 2001;106(2):113-122. doi:10.1016/S0925-4927(01)00074-9 5. Ferri F, Chiarelli AM, Merla A, Gallese V, Costantini M. The body beyond the body: Expectation of a sensory event is enough to induce ownership over a fake hand. Proceedings of the Royal Society B: Biological Sciences. 2013;280(1765). doi:10.5061/dryad.8f251 6. Suzuki K, Garfinkel SN, Critchley HD, Seth AK. Multisensory integration across exteroceptive and interoceptive domains modulates self-experience in the rubber-hand illusion. Neuropsychologia. 2013;51(13):2909-2917. doi:10.1016/j.neuropsychologia.2013.08.014 7. Zeidan F, Grant JA, Brown CA, McHaffie JG, Coghill RC. Mindfulness meditation-related pain relief: Evidence for unique brain mechanisms in the regulation of pain. Neuroscience Letters. 2012;520(2):165-173. doi:10.1016/j.neulet.2012.03.082 8. Al-Obaidi SM, Beattie P, Al-Zoabi B, Al-Wekeel S. The relationship of anticipated pain and fear avoidance beliefs to outcome in patients with chronic low back pain who are not receiving workers’ compensation. Spine. 2005;30(9):1051-1057. doi:10.1097/01.brs.0000160848.94706.83 9. Benedetti F, Mayberg HS, Wager TD, Stohler CS, Zubieta JK. Neurobiological mechanisms of the placebo effect. In: Journal of Neuroscience. Vol 25. Society for Neuroscience; 2005:10390-10402. doi:10.1523/JNEUROSCI.3458-05.2005 10. Gard T, Hölzel BK, Sack AT, et al. Pain attenuation through mindfulness is associated with decreased cognitive control and increased sensory processing in the brain. Cerebral Cortex. 2012;22(11):2692-2702. doi:10.1093/cercor/bhr352 11.Grant JA, Courtemanche J, Rainville P. A non-elaborative mental stance and decoupling of executive and pain-related cortices predicts low pain sensitivity in Zen meditators. Pain. 2011;152(1):150-156. doi:10.1016/j.pain.2010.10.006 12. Kabat-Zinn J, Lipworth L, Burney R. The clinical use of mindfulness meditation for the self-regulation of chronic pain. Journal of Behavioral Medicine. 1985;8(2):163-190. doi:10.1007/BF00845519 13. Kakigi R, Nakata H, Inui K, et al. Intracerebral pain processing in a Yoga Master who claims not to feel pain during meditation. European Journal of Pain. 2005;9(5):581. doi:10.1016/j.ejpain.2004.12.006 14. Steeds CE. The anatomy and physiology of pain. Surgery. 2009;27(12):507-511. doi:10.1016/j.mpsur.2009.10.013 15. Min BK. A thalamic reticular networking model of consciousness. Theoretical Biology and Medical Modelling. 2010;7(1):1-18. doi:10.1186/1742-4682-7-10 16. Hasenkamp W, Wilson-Mendenhall CD, Duncan E, Barsalou LW. Mind wandering and attention during focused meditation: A fine-grained temporal analysis of fluctuating cognitive states. NeuroImage. 2012;59(1):750-760. doi:10.1016/j.neuroimage.2011.07.008 17. Newberg AB, Waldman MR. A neurotheological approach to spiritual awakening. International Journal of Transpersonal Studies. 2019;37(2):119-130. doi:10.24972/ijts.2018.37.2.119 18. Johnstone B, Cohen D, Konopacki K, Ghan C. Selflessness as a Foundation of Spiritual Transcendence: Perspectives From the Neurosciences and Religious Studies. International Journal for the Psychology of Religion. 2016;26(4):287-303. doi:10.1080/10508619.2015.1118328 19. Yaden DB, Haidt J, Hood RW, Vago DR, Newberg AB. The varieties of self-transcendent experience. Review of General Psychology. 2017;21(2):143-160. doi:10.1037/gpr0000102 20. Griffiths RR, Richards WA, McCann U, Jesse R. Psilocybin can occasion mystical-type experiences having substantial and sustained personal meaning and spiritual significance. Psychopharmacology. 2006;187(3):268-283. doi:10.1007/s00213-006-0457-5 21. Griffiths RR, Richards WA, Johnson MW, McCann UD, Jesse R. Mystical-type experiences occasioned by psilocybin mediate the attribution of personal meaning and spiritual significance 14 months later. Journal of Psychopharmacology. 2008;22(6):621-632. doi:10.1177/0269881108094300 22. Serino A, Alsmith A, Costantini M, Mandrigin A, Tajadura-Jimenez A, Lopez C. Bodily ownership and self-location: Components of bodily self-consciousness. Consciousness and Cognition. 2013;22(4):1239-1252. doi:10.1016/j.concog.2013.08.013 23. Tsakiris M, Costantini M, Haggard P. The role of the right temporo-parietal junction in maintaining a coherent sense of one’s body. Neuropsychologia. 2008;46(12):3014-3018. doi:10.1016/j.neuropsychologia.2008.06.004 24. Herzog H, Leie VR, Kuweit T, Rota E, Ludwig K. Biological Psychology/Pharmacopsychology. Published online 1990:182-187.
-
 @ 3bf0c63f:aefa459d
2024-06-13 15:40:18
@ 3bf0c63f:aefa459d
2024-06-13 15:40:18Why relay hints are important
Recently Coracle has removed support for following relay hints in Nostr event references.
Supposedly Coracle is now relying only on public key hints and
kind:10002events to determine where to fetch events from a user. That is a catastrophic idea that destroys much of Nostr's flexibility for no gain at all.- Someone makes a post inside a community (either a NIP-29 community or a NIP-87 community) and others want to refer to that post in discussions in the external Nostr world of
kind:1s -- now that cannot work because the person who created the post doesn't have the relays specific to those communities in their outbox list; - There is a discussion happening in a niche relay, for example, a relay that can only be accessed by the participants of a conference for the duration of that conference -- since that relay is not in anyone's public outbox list, it's impossible for anyone outside of the conference to ever refer to these events;
- Some big public relays, say, relay.damus.io, decide to nuke their databases or periodically delete old events, a user keeps using that big relay as their outbox because it is fast and reliable, but chooses to archive their old events in a dedicated archival relay, say, cellar.nostr.wine, while prudently not including that in their outbox list because that would make no sense -- now it is impossible for anyone to refer to old notes from this user even though they are publicly accessible in cellar.nostr.wine;
- There are topical relays that curate content relating to niche (non-microblogging) topics, say, cooking recipes, and users choose to publish their recipes to these relays only -- but now they can't refer to these relays in the external Nostr world of
kind:1s because these topical relays are not in their outbox lists. - Suppose a user wants to maintain two different identities under the same keypair, say, one identity only talks about soccer in English, while the other only talks about art history in French, and the user very prudently keeps two different
kind:10002events in two different sets of "indexer" relays (or does it in some better way of announcing different relay sets) -- now one of this user's audiences cannot ever see notes created by him with their other persona, one half of the content of this user will be inacessible to the other half and vice-versa. - If for any reason a relay does not want to accept events of a certain kind a user may publish to other relays, and it would all work fine if the user referenced that externally-published event from a normal event, but now that externally-published event is not reachable because the external relay is not in the user's outbox list.
- If someone, say, Alex Jones, is hard-banned everywhere and cannot event broadcast
kind:10002events to any of the commonly used index relays, that person will now appear as banned in most clients: in an ideal world in which clients followednprofileand other relay hints Alex Jones could still live a normal Nostr life: he would print business cards with hisnprofileinstead of annpuband clients would immediately know from what relay to fetch his posts. When other users shared his posts or replied to it, they would include a relay hint to his personal relay and others would be able to see and then start following him on that relay directly -- now Alex Jones's events cannot be read by anyone that doesn't already know his relay.
- Someone makes a post inside a community (either a NIP-29 community or a NIP-87 community) and others want to refer to that post in discussions in the external Nostr world of
-
 @ 0edc2f47:730cff1b
2025-04-04 03:37:02
@ 0edc2f47:730cff1b
2025-04-04 03:37:02Chef's notes
This started as a spontaneous kitchen experiment—an amalgamation of recipes from old cookbooks and online finds. My younger daughter wanted to surprise her sister with something quick but fancy ("It's a vibe, Mom."), and this is what we came up with. It’s quickly established itself as a go-to favorite: simple, rich, and deeply satisfying. It serves 4 (or 1, depending on the day; I am not here to judge). Tightly wrapped, it will keep up to 3 days in the fridge, but I bet it won't last that long!
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 0 min
Ingredients
- 1 cup (240mL) heavy whipping cream
- 1/4 cup (24g) cocoa powder
- 5 tbsp (38g) Confectioners (powdered) sugar
- 1/4 tsp (1.25mL) vanilla extract (optional)
- Flaky sea salt (optional, but excellent)
Directions
-
- Whip the cream until frothy.
-
- Sift in cocoa and sugar, fold or gently mix (add vanilla if using).
-
- Whip to medium peaks (or stiff peaks, if that's more your thing). Chill and serve (topped with a touch of sea salt if you’re feeling fancy).
-
 @ 3bf0c63f:aefa459d
2024-06-12 15:26:56
@ 3bf0c63f:aefa459d
2024-06-12 15:26:56How to do curation and businesses on Nostr
Suppose you want to start a Nostr business.
You might be tempted to make a closed platform that reuses Nostr identities and grabs (some) content from the external Nostr network, only to imprison it inside your thing -- and then you're going to run an amazing AI-powered algorithm on that content and "surface" only the best stuff and people will flock to your app.
This will be specially good if you're going after one of the many unexplored niches of Nostr in which reading immediately from people you know doesn't work as you generally want to discover new things from the outer world, such as:
- food recipe sharing;
- sharing of long articles about varying topics;
- markets for used goods;
- freelancer work and job offers;
- specific in-game lobbies and matchmaking;
- directories of accredited professionals;
- sharing of original music, drawings and other artistic creations;
- restaurant recommendations
- and so on.
But that is not the correct approach and damages the freedom and interoperability of Nostr, posing a centralization threat to the protocol. Even if it "works" and your business is incredibly successful it will just enshrine you as the head of a platform that controls users and thus is prone to all the bad things that happen to all these platforms. Your company will start to display ads and shape the public discourse, you'll need a big legal team, the FBI will talk to you, advertisers will play a big role and so on.
If you are interested in Nostr today that must be because you appreciate the fact that it is not owned by any companies, so it's safe to assume you don't want to be that company that owns it. So what should you do instead? Here's an idea in two steps:
- Write a Nostr client tailored to the niche you want to cover
If it's a music sharing thing, then the client will have a way to play the audio and so on; if it's a restaurant sharing it will have maps with the locations of the restaurants or whatever, you get the idea. Hopefully there will be a NIP or a NUD specifying how to create and interact with events relating to this niche, or you will write or contribute with the creation of one, because without interoperability none of this matters much.
The client should work independently of any special backend requirements and ideally be open-source. It should have a way for users to configure to which relays they want to connect to see "global" content -- i.e., they might want to connect to
wss://nostr.chrysalisrecords.com/to see only the latest music releases accredited by that label or towss://nostr.indiemusic.com/to get music from independent producers from that community.- Run a relay that does all the magic
This is where your value-adding capabilities come into play: if you have that magic sauce you should be able to apply it here. Your service, let's call it
wss://magicsaucemusic.com/, will charge people or do some KYM (know your music) validation or use some very advanced AI sorcery to filter out the spam and the garbage and display the best content to your users who will request the global feed from it (["REQ", "_", {}]), and this will cause people to want to publish to your relay while others will want to read from it.You set your relay as the default option in the client and let things happen. Your relay is like your "website" and people are free to connect to it or not. You don't own the network, you're just competing against other websites on a leveled playing field, so you're not responsible for it. Users get seamless browsing across multiple websites, unified identities, a unified interface (that could be different in a different client) and social interaction capabilities that work in the same way for all, and they do not depend on you, therefore they're more likely to trust you.
Does this centralize the network still? But this a simple and easy way to go about the matter and scales well in all aspects.
Besides allowing users to connect to specific relays for getting a feed of curated content, such clients should also do all kinds of "social" (i.e. following, commenting etc) activities (if they choose to do that) using the outbox model -- i.e. if I find a musician I like under
wss://magicsaucemusic.comand I decide to follow them I should keep getting updates from them even if they get banned from that relay and start publishing onwss://nos.lolorwss://relay.damus.ioor whatever relay that doesn't even know what music is.The hardcoded defaults and manual typing of relay URLs can be annoying. But I think it works well at the current stage of Nostr development. Soon, though, we can create events that recommend other relays or share relay lists specific to each kind of activity so users can get in-app suggestions of relays their friends are using to get their music from and so on. That kind of stuff can go a long way.
-
 @ 3bf0c63f:aefa459d
2024-05-24 12:31:40
@ 3bf0c63f:aefa459d
2024-05-24 12:31:40About Nostr, email and subscriptions
I check my emails like once or twice a week, always when I am looking for something specific in there.
Then I go there and I see a bunch of other stuff I had no idea I was missing. Even many things I wish I had seen before actually. And sometimes people just expect and assume I would have checked emails instantly as they arrived.
It's so weird because I'm not making a point, I just don't remember to open the damn "gmail.com" URL.
I remember some people were making some a Nostr service a while ago that sent a DM to people with Nostr articles inside -- or some other forms of "subscription services on Nostr". It makes no sense at all.
Pulling in DMs from relays is exactly the same process (actually slightly more convoluted) than pulling normal public events, so why would a service assume that "sending a DM" was more likely to reach the target subscriber when the target had explicitly subscribed to that topic or writer?
Maybe due to how some specific clients work that is true, but fundamentally it is a very broken assumption that comes from some fantastic past era in which emails were 100% always seen and there was no way for anyone to subscribe to someone else's posts.
Building around such broken assumptions is the wrong approach. Instead we should be building new flows for subscribing to specific content from specific Nostr-native sources (creators directly or manual or automated curation providers, communities, relays etc), which is essentially what most clients are already doing anyway, but specifically Coracle's new custom feeds come to mind now.
This also reminds me of the interviewer asking the Farcaster creator if Farcaster made "email addresses available to content creators" completely ignoring all the cryptography and nature of the protocol (Farcaster is shit, but at least they tried, and in this example you could imagine the interviewer asking the same thing about Nostr).
I imagine that if the interviewer had asked these people who were working (or suggesting) the Nostr DM subscription flow they would have answered: "no, you don't get their email addresses, but you can send them uncensorable DMs!" -- and that, again, is getting everything backwards.
-
 @ 2b24a1fa:17750f64
2025-04-01 08:09:55
@ 2b24a1fa:17750f64
2025-04-01 08:09:55 -
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 812cff5a:5c40aeeb
2025-04-01 02:57:20
@ 812cff5a:5c40aeeb
2025-04-01 02:57:20مقدمة
في عالم اليوم الرقمي، تبرز منصات جديدة تهدف إلى تعزيز تجربة القراءة والتواصل بين محبي الكتب. تُعَدُّ Bookstr.xyz واحدة من هذه المنصات المبتكرة التي تسعى لربط القرّاء عبر شبكة Nostr، مما يمنحهم سيادة كاملة على بياناتهم ويتيح لهم بناء علاقات جديدة مع محبي الكتب الآخرين. 
الميزات الرئيسية لموقع Bookstr
- التحكم الكامل بالبيانات: توفر Bookstr.xyz للمستخدمين القدرة على التحكم الكامل في بياناتهم الشخصية، مما يضمن خصوصية وأمان المعلومات.
- التكامل مع Open Library: تستخدم المنصة واجهة برمجة التطبيقات الخاصة بـ Open Library للحصول على معلومات شاملة حول الكتب، مما يتيح للمستخدمين الوصول إلى مجموعة واسعة من البيانات الموثوقة.
- التواصل الاجتماعي: من خلال شبكة Nostr، يمكن للمستخدمين التواصل مع قرّاء آخرين، تبادل التوصيات، ومناقشة الكتب المفضلة لديهم. 
ما الذي يجعلها فريدة؟
تتميز Bookstr.xyz بدمجها بين مزايا الشبكات الاجتماعية ومصادر بيانات الكتب المفتوحة، مما يخلق بيئة تفاعلية وغنية بالمعلومات لمحبي القراءة. استخدامها لشبكة Nostr يمنح المستخدمين حرية أكبر في التحكم بتجربتهم الرقمية مقارنة بالمنصات التقليدية. 
جرب Bookstr
تُعَدُّ Bookstr.xyz إضافة قيمة لعالم القراءة الرقمي، حيث تجمع بين مزايا الشبكات الاجتماعية ومصادر البيانات المفتوحة، مع التركيز على خصوصية المستخدم والتحكم في البيانات. إذا كنت من عشاق الكتب وتبحث عن منصة تفاعلية وآمنة، فقد تكون Bookstr.xyz الخيار المثالي لك.
شاركوا كتبكم المفضلة!!
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 878dff7c:037d18bc
2025-03-31 21:29:17
@ 878dff7c:037d18bc
2025-03-31 21:29:17Dutton Proposes Easing Home Loan Regulations
Summary:
Opposition Leader Peter Dutton plans to challenge the Albanese government by proposing changes to lending rules aimed at making it easier for first-time home buyers to access loans. The proposed adjustments include reducing serviceability buffers and addressing the treatment of HELP debt to improve housing access. Dutton argues that current regulations create a bias favoring inherited wealth, making it difficult for new buyers to enter the housing market. These proposals come as the Reserve Bank of Australia prepares for its upcoming interest rate decision, with the current cash rate target at 4.1% and predictions of a cut in May. Treasurer Jim Chalmers highlights the government's progress, noting falling inflation, rising real wages, and improving economic growth.
Sources: News.com.au - 1 April 2025, The Australian - 1 April 2025
Australia's Housing Market Hits New Record High
Summary:
Australia's property prices reached a new peak in March, following a rate cut that enhanced buyer optimism. CoreLogic reported a 0.4% monthly increase, bringing the average national property price to A$820,331. All capital cities, except Hobart, experienced price gains, with Sydney and Melbourne rising by 0.3% and 0.5%, respectively. The rate cut slightly improved borrowing capacity and mortgage serviceability. However, the sustainability of this upward trend is uncertain due to persistent affordability issues. While the market rebounded with the February rate cut by the Reserve Bank of Australia, significant improvements in home loan serviceability are necessary for substantial market growth.
Source: Reuters - 1 April 2025
AI Revolutionizes Business Operations
Summary:
Artificial intelligence (AI) is transforming business practices globally, with applications ranging from administrative task automation to strategic decision-making enhancements. Companies are increasingly integrating AI to streamline operations and gain competitive advantages. This shift necessitates a focus on ethical AI deployment and workforce upskilling to address potential job displacement.
Sources: Financial Times - April 1, 2025
Criticism of Bureau of Meteorology's Forecasting Capabilities
Summary:
The Bureau of Meteorology is facing criticism for inadequate weather radar coverage in western Queensland, which has led to unreliable forecasting during the recent floods. Federal Opposition Leader Peter Dutton has pledged $10 million for a new radar system to enhance forecasting accuracy, while local officials emphasize the need for improved infrastructure to better prepare for future natural disasters.
Sources: The Australian - April 1, 2025
Coalition Pledges $10 Million for Western Queensland Weather Radar
Summary:
As part of the federal election campaign, Opposition Leader Peter Dutton has promised $10 million for a new weather radar system in flood-affected western Queensland. This initiative aims to improve weather forecasting and preparedness in the region. Meanwhile, Prime Minister Anthony Albanese has pledged $200 million for an upgrade to the St John of God Midland hospital in Perth, emphasizing healthcare improvements. Both leaders are focusing on key regional investments as the election approaches.
Source: The Guardian - April 1, 2025
Emergency Services Conduct Rescues Amid Queensland Floods
Summary:
Emergency services in Queensland have conducted over 40 rescues as floodwaters continue to rise, submerging communities and causing extensive damage. Efforts are focused on delivering essential supplies, evacuating residents, and ensuring the safety of those affected by the severe weather conditions.
Sources: The Courier-Mail - April 1, 2025
Six Key Crises Facing Australia Before the Election
Summary:
As the election nears, voters remain largely unaware of six looming crises that could significantly impact the nation. These include over-reliance on volatile commodity exports, challenges in renewable energy implementation, potential currency depreciation, and reduced foreign investment. Both major parties have focused on immediate cost-of-living relief, overshadowing these critical issues that demand urgent attention.
Sources: The Australian - April 1, 2025
Debate Intensifies Over Australia's Commitment to AUKUS
Summary:
Former Defence Department Secretary Dennis Richardson has urged Australia to persist with the AUKUS submarine agreement despite concerns about the reliability of the U.S. under President Donald Trump. Richardson warns that abandoning the deal now would undermine decades of defense planning. However, critics, including former Prime Minister Malcolm Turnbull, question the feasibility and advisability of the agreement, suggesting alternatives such as partnering with France for submarine development.
Sources: The Guardian - April 1, 2025, The Australian - April 1, 2025
China Delays $23B Sale of Panama Canal Ports to US-Backed Consortium
Summary:
China has postponed the $23 billion sale of 43 global ports, including critical facilities at both ends of the Panama Canal, to a consortium led by US investment firm BlackRock. The delay follows an investigation by China’s State Administration for Market Regulation into potential anti-monopoly law violations. This unexpected move has heightened tensions between China and the US, as President Trump viewed the sale as a strategic victory in the ongoing power struggle between the two nations. The deal's future remains uncertain, causing political and economic ripples amid China's significant annual "two sessions" gathering.
Sources: New York Post - March 31, 2025
Australian Government's Handling of Suspected Chinese Spy Ship Raises Concerns
Summary:
The Australian government has assigned the monitoring of the suspected Chinese spy ship, Tan Suo Yi Hao, to the Australian Border Force, despite Prime Minister Anthony Albanese's assertion that the Australian Defence Force was managing the situation. Security experts believe the vessel is collecting undersea data for future Chinese submarine operations, highlighting national security concerns during an election period. The handling of this issue has led to criticism and confusion over which agency is in charge, with opposition figures condemning the government's lack of detailed information.
Sources: The Australian - April 1, 2025
Concerns Rise Over Schoolchildren Accessing Weight Loss Drugs
Summary:
Health experts are alarmed by reports of Australian schoolchildren accessing weight loss medications like semaglutide (Ozempic) through various means, including online purchases and taking them from home supplies. These substances are being linked to secretive and harmful diet clubs within schools, posing severe health risks such as potentially fatal overdoses. Advocates emphasize the need for stricter regulation of weight loss products and call for mandatory education programs on eating disorders in schools to address the growing issue.
Sources: The Courier-Mail - 1 April 2025
Recycling Plant Explosion Highlights Dangers of Improper Aerosol Disposal
Summary:
A Victorian company has been fined $35,000 after an explosion at its recycling plant injured six workers. The incident occurred when pressurized aerosol cans were improperly shredded, causing flames to spread up to 18 meters. Investigations revealed that the company failed to implement safety procedures such as emptying or puncturing the cans before shredding and ensuring adequate ventilation. This case underscores the critical importance of adhering to safety protocols when handling hazardous materials.
Sources: Herald Sun - 1 April 2025
Australia Enforces New Tobacco Controls from April 1
Summary:
As of April 1, 2025, Australia has implemented stringent tobacco control measures, including health warnings printed directly on individual cigarettes. These warnings feature phrases such as "CAUSES 16 CANCERS" and "DAMAGES YOUR LUNGS." Additionally, new graphic warnings on cigarette packs and health promotion inserts aim to encourage smoking cessation and raise awareness about the dangers of tobacco use.
Sources: Mirage News - April 1, 2025, 9News - April 1, 2025
OPEC+ Increases Oil Production Amid Global Uncertainties
Summary:
OPEC+ has announced the gradual unwinding of voluntary production cuts starting April 1, 2025, aiming to restore 2.2 million barrels per day of output by September 2026. Despite this increase, factors such as tighter U.S. sanctions on Iran and Russia, potential sanctions on Venezuelan oil buyers, and fears of a tariff-induced recession have sustained oil prices. Analysts predict limited downside risks to oil prices due to significant supply threats, mainly from Iran and Venezuela. While some strength in oil prices is expected during the summer, concerns over tariff-induced demand weakness persist.
Sources: MarketWatch - April 1, 2025
Iconic Australian Locations Declared 'No Go Zones'
Summary:
Several iconic Australian locations, including Uluru, Kakadu National Park, Cape York Peninsula, and others, are increasingly being declared "no go zones" due to cultural, environmental, and safety concerns. These measures aim to preserve the cultural significance and environmental integrity of these landmarks and ensure public safety. While traditional owners and local authorities support these restrictions to protect cultural heritage, debates have arisen over tourists' rights and the impact on local tourism industries. Sources: News.com.au - April 1, 2025
The Joe Rogan Experience #2297: Francis Foster & Konstantin Kisin
Summary:
In episode #2297 of The Joe Rogan Experience, Joe Rogan welcomes comedians and commentators Francis Foster and Konstantin Kisin, hosts of the podcast Triggernometry. The episode delivers a wide-ranging conversation covering free speech, comedy, media narratives, and societal tensions in the modern world.
Interesting Discussions and Insights:
-
The State of Comedy:\ The trio discusses how comedy has changed in recent years, especially under the weight of cancel culture. They explore how comedians are navigating cultural sensitivities while still trying to push boundaries and remain authentic.
-
Free Speech and Censorship:\ Konstantin and Francis share their experiences with censorship and self-censorship, emphasizing the risks of suppressing ideas, even if they’re controversial. They advocate for robust debate as a cornerstone of democracy.
-
Migration and Identity Politics:\ The conversation touches on immigration policies in the UK and broader Western world, discussing how political correctness often silences real concerns. Both guests, with immigrant backgrounds, offer nuanced perspectives on national identity and inclusion.
-
Media and Narrative Control:\ Joe, Francis, and Konstantin dive into how media outlets often frame stories with ideological slants, and the dangers of relying on one-sided narratives in forming public opinion.
-
Creating Triggernometry:\ The guests talk about why they launched their podcast — to have honest, open conversations with a wide range of thinkers, especially those often excluded from mainstream platforms.
Key Takeaways:
- Honest conversation is essential for a healthy society, even when it's uncomfortable.
- Comedy still holds power to critique society but faces mounting challenges from cultural pressures.
- Free speech should be defended not just in principle, but in everyday life and dialogue.
- The media landscape is increasingly polarized, and critical thinking is more important than ever.
-
-
 @ 3bf0c63f:aefa459d
2024-03-19 15:35:35
@ 3bf0c63f:aefa459d
2024-03-19 15:35:35Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ 78b3c1ed:5033eea9
2025-04-29 04:04:19
@ 78b3c1ed:5033eea9
2025-04-29 04:04:19Umbrel Core-lightning(以下CLNと略す)を運用するにあたり役に立ちそうなノウハウやメモを随時投稿します。
・configファイルを用意する Umbrelのアプリとして必要な設定はdocker-compose.ymlで指定されている。 それ以外の設定をしたい場合configファイルに入れると便利。 configファイルの置き場所は /home/umbrel/umbrel/app-data/core-lightning/data/lightningd ここにtouch configとでもやってファイルをつくる。
cd /home/umbrel/umbrel/app-data/core-lightning/data/lightningd touch config以下内容をひな型として使ってみてください。 行頭に#があるとコメント行になります。つまり.iniフォーマット。 /home/umbrel/umbrel/app-data/core-lightning/data/lightningd/config ```[General options]
[Bitcoin control options]
[Lightning daemon options]
[Lightning node customization options]
[Lightning channel and HTLC options]
[Payment control options]
[Networking options]
[Lightning Plugins]
[Experimental Options]
``` configに設定できる内容は以下を参照 https://lightning.readthedocs.io/lightningd-config.5.html セクションを意味する[]があるけれどもこれは私(tanakei)が意図的に見やすく区別しやすくするために付けただけ。これら行の#は外さない。
・configの設定をCLNに反映させる appスクリプトでCLNを再起動すると反映することができる。 configを書き換えただけでは反映されない。
cd /home/umbrel/umbrel/scripts ./app restart core-lightning・ログをファイルに出力させる
以下の場所でtouch log.txtとしてlog.txtファイルを作る。 /home/umbrel/umbrel/app-data/core-lightning/data/lightningd
cd /home/umbrel/umbrel/app-data/core-lightning/data/lightningd touch log.txt次にconfigの[Lightning daemon options]セクションにlog-fileを追加する。 ```[Lightning daemon options]
log-file=/data/.lightning/log.txt ``` ※Dockerによって/home/umbrel/umbrel/app-data/core-lightning/data/lightningd は /data/.lightning として使われている。
・addrとbind-addrの違い どちらも着信用のインターフェースとポートの設定。addrは指定したホストIPアドレス:ポート番号をノードURIに含めて公開する(node_announcementのuris)。bind-addrは公開しない。
・実験的機能のLN Offerを有効にする configの[Experimental Options]セクションに以下を追加する。 ```
[Experimental Options]
experimental-onion-messages experimental-offers ``` ※ v24.08でexperimental-onion-messageは廃止されデフォルト有効であり、上記設定の追加は不要になりました。 ※ v21.11.1 では experimental-offersは廃止されデフォルト有効であり、上記設定の追加は不要になりました。 もう実験扱いじゃなくなったのね...
・完全にTorでの発信オンリーにする UmbrelはなぜかCLNの発信をClearnetとTorのハイブリッドを許している。それは always-use-proxy=true の設定がないから。(LNDは発着信Torのみなのに) なのでこの設定をconfigに追加してCLNも発着進Torのみにする。 ```
[Networking options]
always-use-proxy=true ```
・任意のニーモニックからhsm_secretを作る CLNのhsm_secretはLNDのwallet.dbのようなもの。ノードで使う様々な鍵のマスター鍵となる。Umbrel CLNはこのhsm_secretファイルを自動生成したものを使い、これをバックアップするためのニーモニックを表示するとかそういう機能はない。自分で作って控えてあるニーモニックでhsm_secretを作ってしまえばこのファイルが壊れてもオンチェーン資金は復旧はできる。
1.CLNインストール後、dockerコンテナに入る
docker exec -it core-lightning_lightningd_1 bash2.lightning-hsmtoolコマンドを使って独自hsm_secretを作る ``` cd data/.lightning/bitcoin lightning-hsmtool generatehsm my-hsm_secret・上記コマンドを実行するとニーモニックの言語、ニーモニック、パスフレーズの入力を催促される。 Select your language: 0) English (en) 1) Spanish (es) 2) French (fr) 3) Italian (it) 4) Japanese (jp) 5) Chinese Simplified (zhs) 6) Chinese Traditional (zht) Select [0-7]: 0 ※定番の英単語なら0を入力 Introduce your BIP39 word list separated by space (at least 12 words): <ニーモニックを入力する> Warning: remember that different passphrases yield different bitcoin wallets. If left empty, no password is used (echo is disabled). Enter your passphrase: <パスフレーズを入力する> ※パスフレーズ不要ならそのままエンターキーを押す。 New hsm_secret file created at my-hsm_secret Use the
encryptcommand to encrypt the BIP32 seed if neededコンテナから抜ける exit
3.appスクリプトでCLNを止めて、独自hsm_secret以外を削除 ※【重要】いままで使っていたhsm_secretを削除する。もしチャネル残高、ウォレット残高があるならチャネルを閉じて資金を退避すること。自己責任!cd ~/umbrel/scripts/ ./app stop core-lightningcd ~/umbrel/app-data/core-lightning/data/lightningd/bitcoin rm gossip_store hsm_secret lightningd.sqlite3 lightning-rpc mv my-hsm_secret hsm_secret
4.appスクリプトでCLNを再開するcd ~/umbrel/scripts/ ./app start core-lightning ```【補記】 hsm_secret作成につかうニーモニックはBIP39で、LNDのAezeedと違って自分が作成されたブロック高さというものを含んでいない。新規でなくて復元して使う場合は作成されたブロック高さからブロックチェーンをrescanする必要がある。 configの1行目にrescanオプションを付けてCLNをリスタートする。 ``` // 特定のブロック高さを指定する場合はマイナス記号をつける rescan=-756000
// 現在のブロック高さから指定ブロック分さかのぼった高さからrescanする rescan=10000 ※現在の高さが760,000なら10000指定だと750,000からrescan ```
・clnrestについて core-lightningでREST APIを利用したい場合、別途c-lightning-restを用意する必要があった。v23.8から標準でclnrestというプラグインがついてくる。pythonで書かれていて、ソースからビルドした場合はビルド完了後にpip installでインストールする。elementsproject/lightningdのDockerイメージではインストール済みになっている。 (v25.02からgithubからバイナリをダウンロードしてきた場合はpip install不要になったようだ) このclnrestを使うにはcreaterunesコマンドでruneというLNDのマカロンのようなものを作成する必要がある。アプリ側でこのruneとREST APIを叩いてcore-lightningへアクセスすることになる。 自分が良く使っているLNbitsやスマホアプリZeus walletはclnrestを使う。まだclnrestに対応していないアプリもあるので留意されたし。
・Emergency recoverについて LNDのSCBのようなもの。ファイル名はemergency.recover チャネルを開くと更新される。 hsm_secretとこのファイルだけを置いてCLNを開始すると自動でこのファイルから強制クローズするための情報が読み出されてDLPで相手から強制クローズするような仕組み。この機能はv0.12から使える。
動作確認してみた所、LNDのSCBに比べるとかなり使いづらい。 1. CLNがTor発信だとチャネルパートナーと接続できない。 Clearnet発信できても相手がTorのみノードならTor発信せざるを得ない。 相手と通信できなければ資金回収できない。 2. 相手がLNDだとなぜか強制クローズされない。相手がCLNならできる。
つまり、自分と相手がClearnetノードでかつ相手もCLNならば Emergency recoverで強制クローズして資金回収できる。こんな条件の厳しい復旧方法がマジで役に立つのか?
v0.11以降ならばLNDのchannel.dbに相当するlightningd.sqlite3をプライマリ・セカンダリDBと冗長化できるので、セカンダリDBをNFSで保存すればUmbrelのストレージが壊れてもセカンダリDBで復旧できる。そのためemergerncy.recoverを使う必要がないと思われる。
・LN offer(BOLT#12)ついて 使いたいなら 1.publicチャネルを開く publicチャネルを開けばチャネルとノードの情報(channel_announcement, node_announcement)が他ノードに伝わる。送金したい相手がこの情報を元に経路探索する。 2.その後しばらく待つ CLNノードを立てたばかりだと経路探索するに十分なチャネルとノードの情報が揃ってない。せめて1日は待つ。
LNURLの場合インボイスをhttpsで取得するが、OfferはLN経由で取得する。そのためにチャネルとノードの情報が必要。privateチャネルばかりのノードはチャネル情報もそうだがノード情報も出さない。 Offerで使えるBlind pathという機能なら中間ノードIDを宛先ノードとすることが可能で、これならチャネルとノード情報を公開しなくても受けとれるのだがCLNは対応してない模様(2025年1月現在) CLNでOfferで受け取るにはチャネルとノード情報を公開する必要がある。そのためpublicチャネルを開く。公開されていれば良いのでTorでもOK。クリアネットで待ち受けは必須ではない。
・hsm_sercretとニーモニック lightning-hsmtoolを使うとニーモニックからhsm_secretを作れる。ニーモニックからシードを作ると64バイト。これはニーモニックおよびソルトにパスフレーズをPBKDF2(HMAC-SHA512を2048回)にかけると512ビット(64バイト)のシードができる。しかしhsm_secretは32バイト。CLNでは64バイトの最初の32バイトをhsm_secretとして利用しているみたい。 このhsm_secretにHMAC-SHA512をかけて512ビットとした値がウォレットのマスター鍵となる。なのでhsm_secret自体がBIP-32でいうマスターシードそのものではない。 sparrow walletにCLNのウォレットを復元したい場合は lightning-hsmtool dumponchaindescriptors --show-secrets
とやってディスクリプターウォレットを出力。出力内容にマスター鍵(xprv~)があるので、これをインポートする。導出パス設定はm/0とする。sparrowが残りを補完してm/0/0/0, m/0/0/1とやってくれる。 <おまけ> configファイルのサンプル。Umbrelを使わない場合は以下のサンプルが役に立つはず。上記のelementsproject/lightningdならば/root/.lightningに任意のディレクトリをマウントしてそのディレクトリにconfigを置く。 ```
[General options]
不可逆なDBアップグレードを許可しない
database-upgrade=false
[Bitcoin control options]
network=bitcoin bitcoin-rpcconnect=
bitcoin-rpcport= bitcoin-rpcuser= bitcoin-rpcpassword= [Lightning daemon options]
postgresを使う場合
wallet=postgres://USER:PASSWORD@HOST:PORT/DB_NAME
bookkeeper-db=postgres://USER:PASSWORD@HOST:PORT/DB_NAME
sqlite3を使う場合。デフォルトはこちらで以下の設定が無くても~/.lightning/bitconに自動で作成される。
wallet=sqlite3:///home/USERNAME/.lightning/bitcoin/lightningd.sqlite3
bookkeeper-db=sqlite3:///home/USERNAME/.lightning/bitcoin/accounts.sqlite3
ログファイルは自動で作成されない
log-file=/home/USERNAME/.lightning/lightningd-log
log-level=debug
[Lightning node customization options]
alias=
rgb= 固定手数料。ミリサトシで指定。
fee-base=1000000
変動手数料。ppmで指定。
fee-per-satoshi=0
最小チャネルキャパシティ(sats)
min-capacity-sat=100000
HTLC最少額。ミリサトシで指定。
htlc-minimum-msat=1000
[Lightning channel and HTLC options]
large-channels # v23.11よりデフォルトでラージチャネルが有効。
チャネル開設まで6承認
funding-confirms=6
着信できるHTLCの数。開いたら変更できない。1~483 (デフォルトは 30) の範囲にする必要があります
max-concurrent-htlcs=INTEGER
アンカーチャネルを閉じるためにウォレットに保持しておく資金。デフォルトは 25,000sat
チャネルを"忘れる(forget)"するまではリザーブされる模様。forgetはチャネル閉じてから100ブロック後
min-emergency-msat=10000000
[Cleanup control options]
autoclean-cycle=3600 autoclean-succeededforwards-age=0 autoclean-failedforwards-age=0 autoclean-succeededpays-age=0 autoclean-failedpays-age=0 autoclean-paidinvoices-age=0 autoclean-expiredinvoices-age=0
[Payment control options]
disable-mpp
[Networking options]
bind-addrだとアナウンスしない。
bind-addr=0.0.0.0:9375
tor
proxy=
: always-use-proxy=true Torの制御ポート。addr=statictor だとhidden serviceをノードURIとして公開する。
addr=statictor:
: tor-service-password= experimental-websocket-portは廃止された。bind-addr=ws:が代替。
bind-addr=ws:
:2106 clnrestプラグイン, REST API
clnrest-host=0.0.0.0 clnrest-port=3010 clnrest-protocol=http
v24.11よりgrpcはデフォルト有効
grpc-host=0.0.0.0 grpc-port=9736
[Lightning Plugins]
[Experimental Options]
experimental-onion-messages # v24.08で廃止。デフォルト有効
experimental-offers # v24.11.1で廃止。デフォルト有効
流動性広告からチャネルを開くときにexperimental-dual-fundが必要らしい。
experimental-dual-fund
experimental-splicing
experimental-peer-storage
```
-
 @ 3bf0c63f:aefa459d
2024-03-19 13:07:02
@ 3bf0c63f:aefa459d
2024-03-19 13:07:02Censorship-resistant relay discovery in Nostr
In Nostr is not decentralized nor censorship-resistant I said Nostr is centralized. Peter Todd thinks it is centralized by design, but I disagree.
Nostr wasn't designed to be centralized. The idea was always that clients would follow people in the relays they decided to publish to, even if it was a single-user relay hosted in an island in the middle of the Pacific ocean.
But the Nostr explanations never had any guidance about how to do this, and the protocol itself never had any enforcement mechanisms for any of this (because it would be impossible).
My original idea was that clients would use some undefined combination of relay hints in reply tags and the (now defunct)
kind:2relay-recommendation events plus some form of manual action ("it looks like Bob is publishing on relay X, do you want to follow him there?") to accomplish this. With the expectation that we would have a better idea of how to properly implement all this with more experience, Branle, my first working client didn't have any of that implemented, instead it used a stupid static list of relays with read/write toggle -- although it did publish relay hints and kept track of those internally and supportedkind:2events, these things were not really useful.Gossip was the first client to implement a truly censorship-resistant relay discovery mechanism that used NIP-05 hints (originally proposed by Mike Dilger) relay hints and
kind:3relay lists, and then with the simple insight of NIP-65 that got much better. After seeing it in more concrete terms, it became simpler to reason about it and the approach got popularized as the "gossip model", then implemented in clients like Coracle and Snort.Today when people mention the "gossip model" (or "outbox model") they simply think about NIP-65 though. Which I think is ok, but too restrictive. I still think there is a place for the NIP-05 hints,
nprofileandneventrelay hints and specially relay hints in event tags. All these mechanisms are used together in ZBD Social, for example, but I believe also in the clients listed above.I don't think we should stop here, though. I think there are other ways, perhaps drastically different ways, to approach content propagation and relay discovery. I think manual action by users is underrated and could go a long way if presented in a nice UX (not conceived by people that think users are dumb animals), and who knows what. Reliance on third-parties, hardcoded values, social graph, and specially a mix of multiple approaches, is what Nostr needs to be censorship-resistant and what I hope to see in the future.
-
 @ 975e4ad5:8d4847ce
2025-04-29 08:26:50
@ 975e4ad5:8d4847ce
2025-04-29 08:26:50With the advancement of quantum computers, a new threat emerges for the security of cryptocurrencies and blockchain technologies. These powerful machines have the potential to expose vulnerabilities in traditional cryptographic systems, which could jeopardize the safety of digital wallets. But don’t worry—modern wallets are already equipped to handle this threat with innovative solutions that make your funds nearly impossible to steal, even by a quantum computer. Let’s explore how this works and why you can rest easy.
The Threat of Quantum Computers
To understand how wallets protect us, we first need to grasp what makes quantum computers so dangerous. At the core of most cryptocurrencies, like Bitcoin, lies public and private key cryptography. The public key (or address) is like your bank account number—you share it to receive funds. The private key is like your PIN—it allows you to send funds and must remain secret.
Traditional cryptography, such as the ECDSA algorithm, relies on mathematical problems that are extremely difficult to solve with conventional computers. For instance, deriving a private key from a public key is practically impossible, as it would take millions of years of computation. However, quantum computers, thanks to algorithms like Shor’s, can significantly speed up this process. Theoretically, a sufficiently powerful quantum computer could uncover a private key from a public key in minutes or even seconds.
This is a problem because if someone gains access to your private key, they can send all your funds to their own address. But here’s the good news—modern wallets use a clever solution to render this threat powerless.
How Do Wallets Protect Us?
One of the most effective defenses against quantum computers is the use of one-time addresses in wallets. This means that for every transaction—whether receiving or sending funds—the wallet automatically generates a new public address. The old address, once used, remains in the transaction history but no longer holds any funds, as they are transferred to a new address.
Why Does This Work?
Imagine you’re sending or receiving cryptocurrency. Your wallet creates a new address for that transaction. After the funds are sent or received, that address becomes “used,” and the wallet automatically generates a new one for the next transaction. If a quantum computer manages to derive the private key from the public address of the used address, it will find nothing—because that address is already empty. Your funds are safely transferred to a new address, whose public key has not yet been exposed.
This strategy is known as HD (Hierarchical Deterministic) wallets. It allows the wallet to generate an infinite number of addresses from a single master key (seed) without compromising security. Each new address is unique and cannot be linked to the previous ones, making it impossible to trace your funds, even with a quantum computer.
Automation Makes It Effortless
The best part? You don’t need to worry about this process—it’s fully automated. When you use a modern wallet like MetaMask, Ledger, Trezor, or software wallets for Bitcoin, everything happens behind the scenes. You simply click “receive” or “send,” and the wallet takes care of generating new addresses. There’s no need to understand the complex technical details or manually manage your keys.
For example:
- You want to receive 0.1 BTC. Your wallet provides a new address, which you share with the sender.
- After receiving the funds, the wallet automatically prepares a new address for the next transaction.
- If you send some of the funds, the remaining amount (known as “change”) is sent to another new address generated by the wallet.
This system ensures that public addresses exposed on the blockchain no longer hold funds, making quantum attacks pointless.
Additional Protection: Toward Post-Quantum Cryptography
Beyond one-time addresses, blockchain developers are also working on post-quantum cryptography—algorithms that are resistant to quantum computers. Some blockchain networks are already experimenting with such solutions, like algorithms based on lattices (lattice-based cryptography). These methods don’t rely on the same mathematical problems that quantum computers can solve, offering long-term protection.
In the meantime, one-time addresses combined with current cryptographic standards provide enough security to safeguard your funds until post-quantum solutions become widely adopted.
Why You Shouldn’t Worry
Modern wallets are designed with the future in mind. They not only protect against today’s threats but also anticipate future risks, such as those posed by quantum computers. One-time addresses make exposed public keys useless to hackers, and automation ensures you don’t need to deal with the technicalities. HD wallets, which automatically generate new addresses, make the process seamless and secure for users.
Public key exposure only happens when necessary, reducing the risk of attacks, even from a quantum computer. In conclusion, while quantum computers pose a potential threat, modern wallets already offer effective solutions that make your cryptocurrencies nearly impossible to steal. With one-time addresses and the upcoming adoption of post-quantum cryptography, you can be confident that your funds are safe—today and tomorrow.
-
 @ 3bf0c63f:aefa459d
2024-01-29 02:19:25
@ 3bf0c63f:aefa459d
2024-01-29 02:19:25Nostr: a quick introduction, attempt #1
Nostr doesn't have a material existence, it is not a website or an app. Nostr is just a description what kind of messages each computer can send to the others and vice-versa. It's a very simple thing, but the fact that such description exists allows different apps to connect to different servers automatically, without people having to talk behind the scenes or sign contracts or anything like that.
When you use a Nostr client that is what happens, your client will connect to a bunch of servers, called relays, and all these relays will speak the same "language" so your client will be able to publish notes to them all and also download notes from other people.
That's basically what Nostr is: this communication layer between the client you run on your phone or desktop computer and the relay that someone else is running on some server somewhere. There is no central authority dictating who can connect to whom or even anyone who knows for sure where each note is stored.
If you think about it, Nostr is very much like the internet itself: there are millions of websites out there, and basically anyone can run a new one, and there are websites that allow you to store and publish your stuff on them.
The added benefit of Nostr is that this unified "language" that all Nostr clients speak allow them to switch very easily and cleanly between relays. So if one relay decides to ban someone that person can switch to publishing to others relays and their audience will quickly follow them there. Likewise, it becomes much easier for relays to impose any restrictions they want on their users: no relay has to uphold a moral ground of "absolute free speech": each relay can decide to delete notes or ban users for no reason, or even only store notes from a preselected set of people and no one will be entitled to complain about that.
There are some bad things about this design: on Nostr there are no guarantees that relays will have the notes you want to read or that they will store the notes you're sending to them. We can't just assume all relays will have everything — much to the contrary, as Nostr grows more relays will exist and people will tend to publishing to a small set of all the relays, so depending on the decisions each client takes when publishing and when fetching notes, users may see a different set of replies to a note, for example, and be confused.
Another problem with the idea of publishing to multiple servers is that they may be run by all sorts of malicious people that may edit your notes. Since no one wants to see garbage published under their name, Nostr fixes that by requiring notes to have a cryptographic signature. This signature is attached to the note and verified by everybody at all times, which ensures the notes weren't tampered (if any part of the note is changed even by a single character that would cause the signature to become invalid and then the note would be dropped). The fix is perfect, except for the fact that it introduces the requirement that each user must now hold this 63-character code that starts with "nsec1", which they must not reveal to anyone. Although annoying, this requirement brings another benefit: that users can automatically have the same identity in many different contexts and even use their Nostr identity to login to non-Nostr websites easily without having to rely on any third-party.
To conclude: Nostr is like the internet (or the internet of some decades ago): a little chaotic, but very open. It is better than the internet because it is structured and actions can be automated, but, like in the internet itself, nothing is guaranteed to work at all times and users many have to do some manual work from time to time to fix things. Plus, there is the cryptographic key stuff, which is painful, but cool.
-
 @ 3c389c8f:7a2eff7f
2025-03-31 20:38:23
@ 3c389c8f:7a2eff7f
2025-03-31 20:38:23You might see these terms used interchangeably throughout the Nostr network. Since Nostr is a decentralized protocol and not a platform, there is often a lack of consensus around particular terminologies. At times, it's important to differentiate between them, so that you can determine what is being stated. In the truest sense, there is no central entity to maintain a Nostr 'account' on your behalf, though some Nostr-based platforms may offer to do so. There's also no one to verify your 'identity'. This is something that you create, maintain and control. It is 100% yours. In a sense, you verify yourself through your interactions with others, with the network of clients and relays, and by protecting your nsec (secret key). A profile is generally considered to be a single place for displaying your content and any information about yourself that you've chosen to share, but its a little more complicated than that with Nostr. Let's take a closer look at all 3 terms:
Identity:
Your Nostr identity becomes yours from the moment you generate your key pair. The two parts each provide unique perspective and functionality. (Remember, there is no central entity to issue these key pairs. You can screw up and start over. You can maintain multiple key pairs for different purposes. If all of this is new and unfamiliar, start simply with the intention of trial and error.)
Half of the equation is your nsec. As long as you maintain control of that secret key, the identity is yours. You will use it to sign the notes and events that you create on Nostr. You will use it to access functionality of various tools and apps. You can use it to send monetary tips for content you find valuable. The reputation that you build through posting & interacting on Nostr will signal to others what type of person or profile this is, whether it's a genuine person, a bot (good or bad), a collection of works, etc. You might come across information that compares your nsec to a password. While a fair comparison, its important to remember that passwords can be reset, but your private key CANNOT. Lost access or control of your nsec means a loss of control over that identity. When you have decided to establish a more permanent identity, write it down, keep it safe, and use the appropriate security tools for interacting online.
The other half of this equation is your npub. This public key is used to find and display your notes and events to others. In short, your npub is how your identity is viewed by others and your nsec is how you control that identity.
Npub can also act a window into your world for whoever may choose to view it. As mentioned in a previous entry, npub login enables viewing Nostr's notes and other stuff in a read-only mode of any user's follow feed. Clients may or may not support this, some will even allow you to view and subscribe to these feeds while signed in as yourself via this function. It the basis of the metadata for your profile, too.
Profile:
Profile, in general, is a collection of things about you, which you have chosen to share. This might include your bio, chosen display name, other contact information, and a profile photo. Similar to traditional socials, veiwing Nostr profiles often includes a feed of the things you have posted and shared displayed as a single page. People will recognize you based on the aspects of your profile more than they will by your actual identity since an npub is a prefixed random string of characters . Your npub bridges a gap between strictly machine readable data and your human readable name, but it is not as simple as a name and picture. You will choose your photo and display name for your profile as you see fit, making you recognizable. These aspects are easy for copycat scammers to leverage, so your npub will help your friends and followers to verify that you are you, in the event that someone should try to copy your profile.
The Nostr protocol has another profile aspect that is important to know about, but as a general user, you shouldn't have to worry much about it. This is your nprofile. It combines your npub (or the machine readable hex verison of it) with hints to what relays you are using to publish your notes. This helps clients, crawlers, and relays find your stuff for your followers. You may notice nprofile when you share a profile link or used in other actions. When you update your relay list, your client will adjust your nprofile and send a new copy to the appropriate relays. If your believe that a client is not doing that correctly, you can visit metadata.nostr.com and manage it yourself.
Account:
Across Nostr, it is common to see the term 'account' used to refer to the combination of your identity and profile. It is a relatable term, though it may imply that some account issuer exists, but no one issues a Nostr account to you. You create and maintain it yourself.
There are situations where a traditional account will exist, such as with media servers, relay subscriptions, custodial wallet hosts, or NIP-05 providers. These things will almost always be paid services and storage that you choose to use. (Reminder: all of these things are possible to DIY with a little knowhow and an old computer)
What Is The Right Terminology?
There is no simple or correct answer here. Developers and writers will use whatever terms fit their scope and topic. Context will matter, so it's important to differentiate by that more than any actual term.
-
 @ 83279ad2:bd49240d
2025-04-29 05:53:52
@ 83279ad2:bd49240d
2025-04-29 05:53:52test
-
 @ f3873798:24b3f2f3
2025-03-31 20:14:31
@ f3873798:24b3f2f3
2025-03-31 20:14:31Olá, nostrilianos!
O tema de hoje é inteligência artificial (IA), com foco em duas ferramentas que têm se destacado no mercado por sua capacidade de responder perguntas, auxiliar em tarefas e, em alguns casos, até gerar imagens.
Essas tecnologias estão cada vez mais presentes no dia a dia, ajudando desde a correção de textos até pesquisas rápidas e a criação de imagens personalizadas com base em prompts específicos.
Nesse cenário em expansão, duas IAs se sobressaem: o ChatGPT, desenvolvido pela OpenAI, e o Grok, criado pela xAI.
Ambas são ferramentas poderosas, cada uma com seus pontos fortes e limitações, e têm conquistado usuários ao redor do mundo. Neste artigo, compartilho minhas impressões sobre essas duas IAs, baseadas em minha experiência pessoal, destacando suas diferenças e vantagens.
Grok: Destaque na criação de imagens e fontes

O Grok me impressiona especialmente em dois aspectos.
Primeiro, sua capacidade de gerar imagens é um diferencial significativo. Enquanto o ChatGPT tem limitações nesse quesito, o Grok oferece uma funcionalidade mais robusta para criar visuais únicos a partir de prompts, o que pode ser uma vantagem para quem busca criatividade visual.
Segundo, o Grok frequentemente cita fontes ou indica a origem das informações que fornece, o que agrega credibilidade às suas respostas e facilita a verificação dos dados.
ChatGPT: Assertividade e clareza

Por outro lado, o ChatGPT se destaca pela assertividade e pela clareza em suas explicações. Suas respostas tendem a ser mais diretas e concisas, o que é ideal para quem busca soluções rápidas ou explicações objetivas.
Acredito que essa vantagem possa estar ligada ao fato de o ChatGPT estar em operação há mais tempo, tendo passado por anos de aprimoramento e ajustes com base em interações de usuários.Comparação e reflexões.
Em minha experiência, o Grok supera o ChatGPT na geração de imagens e na citação de fontes, enquanto o ChatGPT leva a melhor em precisão e simplicidade nas respostas.
Esses pontos refletem não apenas as prioridades de design de cada IA, mas também o tempo de desenvolvimento e os objetivos de suas respectivas empresas criadoras.
A OpenAI, por trás do ChatGPT, focou em refinamento conversacional, enquanto a xAI, com o Grok, parece investir em funcionalidades adicionais, como a criação de conteúdo visual.
Minha opinião

Não há um vencedor absoluto entre Grok e ChatGPT – a escolha depende do que você precisa. Se seu foco é geração de imagens ou rastreamento de fontes, o Grok pode ser a melhor opção. Se busca respostas rápidas e assertivas, o ChatGPT provavelmente atenderá melhor.
Ambas as IAs são ferramentas incríveis, e o mais fascinante é ver como elas continuam evoluindo, moldando o futuro da interação entre humanos e máquinas.
-
 @ 3bf0c63f:aefa459d
2024-01-15 11:15:06
@ 3bf0c63f:aefa459d
2024-01-15 11:15:06Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados
- **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente. - **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados. - **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua. - **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer. - **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos. - **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas. - **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade). - **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis. - **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade. - **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho. - **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho. - **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma. - **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças. - **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família. - **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente. - **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo). - **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas. - **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente). - **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica. - **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar. - **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico. - **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais. - **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil). - **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória. - **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles. - **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas. - **inflação**: a inflação estimula o endividamento e o consumismo. - **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas. - **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo. -
 @ 378562cd:a6fc6773
2025-03-31 19:20:39
@ 378562cd:a6fc6773
2025-03-31 19:20:39Bitcoin transaction fees might seem confusing, but don’t worry—I’ll break it down step by step in a simple way. 🚀
Unlike traditional bank fees, Bitcoin fees aren’t fixed. Instead, they depend on: ✔️ Transaction size (in bytes, not BTC!) ✔️ Network demand (more traffic = higher fees) ✔️ Fee rate (measured in satoshis per byte)
Let’s dive in! 👇
📌 Why Do Bitcoin Transactions Have Fees? Bitcoin miners process transactions and add them to the blockchain. Fees serve three key purposes:
🔹 Incentivize Miners – They receive fees + block rewards. 🔹 Prevent Spam – Stops the network from being flooded. 🔹 Prioritize Transactions – Higher fees = faster confirmations.
💰 How Are Bitcoin Fees Calculated? Bitcoin fees are not based on the amount of BTC you send. Instead, they depend on how much space your transaction takes up in a block.
🧩 1️⃣ Transaction Size (Bytes, Not BTC!) Bitcoin transactions vary in size (measured in bytes).
More inputs and outputs = larger transactions.
Larger transactions take up more block space, meaning higher fees.
📊 2️⃣ Fee Rate (Sats Per Byte) Fees are measured in satoshis per byte (sat/vB).
You set your own fee based on how fast you want the transaction confirmed.
When demand is high, fees rise as users compete for block space.
⚡ 3️⃣ Network Demand If the network is busy, miners prioritize transactions with higher fees.
Low-fee transactions may take hours or even days to confirm.
🔢 Example: Calculating a Bitcoin Transaction Fee Let’s say: 📦 Your transaction is 250 bytes. 💲 The current fee rate is 50 sat/vB.
Formula: 🖩 Transaction Fee = Size × Fee Rate = 250 bytes × 50 sat/vB = 12,500 satoshis (0.000125 BTC)
💡 If 1 BTC = $60,000, the fee would be: 0.000125 BTC × $60,000 = $7.50
🚀 How to Lower Bitcoin Fees? Want to save on fees? Try these tips:
🔹 Use SegWit Addresses – Reduces transaction size! 🔹 Batch Transactions – Combine multiple payments into one. 🔹 Wait for Low Traffic – Fees fluctuate based on demand. 🔹 Use the Lightning Network – Near-zero fees for small payments.
🏁 Final Thoughts Bitcoin fees aren’t fixed—they depend on transaction size, fee rate, and network demand. By understanding how fees work, you can save money and optimize your transactions!
🔍 Want real-time fee estimates? Check mempool.space for live data! 🚀
-
 @ 3bf0c63f:aefa459d
2024-01-15 11:15:06
@ 3bf0c63f:aefa459d
2024-01-15 11:15:06Anglicismos estúpidos no português contemporâneo
Palavras e expressões que ninguém deveria usar porque não têm o sentido que as pessoas acham que têm, são apenas aportuguesamentos de palavras inglesas que por nuances da história têm um sentido ligeiramente diferente em inglês.
Cada erro é acompanhado também de uma sugestão de como corrigi-lo.
Palavras que existem em português com sentido diferente
- submissão (de trabalhos): envio, apresentação
- disrupção: perturbação
- assumir: considerar, pressupor, presumir
- realizar: perceber
- endereçar: tratar de
- suporte (ao cliente): atendimento
- suportar (uma idéia, um projeto): apoiar, financiar
- suportar (uma função, recurso, característica): oferecer, ser compatível com
- literacia: instrução, alfabetização
- convoluto: complicado.
- acurácia: precisão.
- resiliência: resistência.
Aportuguesamentos desnecessários
- estartar: iniciar, começar
- treidar: negociar, especular
Expressões
- "não é sobre...": "não se trata de..."
Ver também
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16Drivechain
Understanding Drivechain requires a shift from the paradigm most bitcoiners are used to. It is not about "trustlessness" or "mathematical certainty", but game theory and incentives. (Well, Bitcoin in general is also that, but people prefer to ignore it and focus on some illusion of trustlessness provided by mathematics.)
Here we will describe the basic mechanism (simple) and incentives (complex) of "hashrate escrow" and how it enables a 2-way peg between the mainchain (Bitcoin) and various sidechains.
The full concept of "Drivechain" also involves blind merged mining (i.e., the sidechains mine themselves by publishing their block hashes to the mainchain without the miners having to run the sidechain software), but this is much easier to understand and can be accomplished either by the BIP-301 mechanism or by the Spacechains mechanism.
How does hashrate escrow work from the point of view of Bitcoin?
A new address type is created. Anything that goes in that is locked and can only be spent if all miners agree on the Withdrawal Transaction (
WT^) that will spend it for 6 months. There is one of these special addresses for each sidechain.To gather miners' agreement
bitcoindkeeps track of the "score" of all transactions that could possibly spend from that address. On every block mined, for each sidechain, the miner can use a portion of their coinbase to either increase the score of oneWT^by 1 while decreasing the score of all others by 1; or they can decrease the score of allWT^s by 1; or they can do nothing.Once a transaction has gotten a score high enough, it is published and funds are effectively transferred from the sidechain to the withdrawing users.
If a timeout of 6 months passes and the score doesn't meet the threshold, that
WT^is discarded.What does the above procedure mean?
It means that people can transfer coins from the mainchain to a sidechain by depositing to the special address. Then they can withdraw from the sidechain by making a special withdraw transaction in the sidechain.
The special transaction somehow freezes funds in the sidechain while a transaction that aggregates all withdrawals into a single mainchain
WT^, which is then submitted to the mainchain miners so they can start voting on it and finally after some months it is published.Now the crucial part: the validity of the
WT^is not verified by the Bitcoin mainchain rules, i.e., if Bob has requested a withdraw from the sidechain to his mainchain address, but someone publishes a wrongWT^that instead takes Bob's funds and sends them to Alice's main address there is no way the mainchain will know that. What determines the "validity" of theWT^is the miner vote score and only that. It is the job of miners to vote correctly -- and for that they may want to run the sidechain node in SPV mode so they can attest for the existence of a reference to theWT^transaction in the sidechain blockchain (which then ensures it is ok) or do these checks by some other means.What? 6 months to get my money back?
Yes. But no, in practice anyone who wants their money back will be able to use an atomic swap, submarine swap or other similar service to transfer funds from the sidechain to the mainchain and vice-versa. The long delayed withdraw costs would be incurred by few liquidity providers that would gain some small profit from it.
Why bother with this at all?
Drivechains solve many different problems:
It enables experimentation and new use cases for Bitcoin
Issued assets, fully private transactions, stateful blockchain contracts, turing-completeness, decentralized games, some "DeFi" aspects, prediction markets, futarchy, decentralized and yet meaningful human-readable names, big blocks with a ton of normal transactions on them, a chain optimized only for Lighting-style networks to be built on top of it.
These are some ideas that may have merit to them, but were never actually tried because they couldn't be tried with real Bitcoin or inferfacing with real bitcoins. They were either relegated to the shitcoin territory or to custodial solutions like Liquid or RSK that may have failed to gain network effect because of that.
It solves conflicts and infighting
Some people want fully private transactions in a UTXO model, others want "accounts" they can tie to their name and build reputation on top; some people want simple multisig solutions, others want complex code that reads a ton of variables; some people want to put all the transactions on a global chain in batches every 10 minutes, others want off-chain instant transactions backed by funds previously locked in channels; some want to spend, others want to just hold; some want to use blockchain technology to solve all the problems in the world, others just want to solve money.
With Drivechain-based sidechains all these groups can be happy simultaneously and don't fight. Meanwhile they will all be using the same money and contributing to each other's ecosystem even unwillingly, it's also easy and free for them to change their group affiliation later, which reduces cognitive dissonance.
It solves "scaling"
Multiple chains like the ones described above would certainly do a lot to accomodate many more transactions that the current Bitcoin chain can. One could have special Lightning Network chains, but even just big block chains or big-block-mimblewimble chains or whatnot could probably do a good job. Or even something less cool like 200 independent chains just like Bitcoin is today, no extra features (and you can call it "sharding"), just that would already multiply the current total capacity by 200.
Use your imagination.
It solves the blockchain security budget issue
The calculation is simple: you imagine what security budget is reasonable for each block in a world without block subsidy and divide that for the amount of bytes you can fit in a single block: that is the price to be paid in satoshis per byte. In reasonable estimative, the price necessary for every Bitcoin transaction goes to very large amounts, such that not only any day-to-day transaction has insanely prohibitive costs, but also Lightning channel opens and closes are impracticable.
So without a solution like Drivechain you'll be left with only one alternative: pushing Bitcoin usage to trusted services like Liquid and RSK or custodial Lightning wallets. With Drivechain, though, there could be thousands of transactions happening in sidechains and being all aggregated into a sidechain block that would then pay a very large fee to be published (via blind merged mining) to the mainchain. Bitcoin security guaranteed.
It keeps Bitcoin decentralized
Once we have sidechains to accomodate the normal transactions, the mainchain functionality can be reduced to be only a "hub" for the sidechains' comings and goings, and then the maximum block size for the mainchain can be reduced to, say, 100kb, which would make running a full node very very easy.
Can miners steal?
Yes. If a group of coordinated miners are able to secure the majority of the hashpower and keep their coordination for 6 months, they can publish a
WT^that takes the money from the sidechains and pays to themselves.Will miners steal?
No, because the incentives are such that they won't.
Although it may look at first that stealing is an obvious strategy for miners as it is free money, there are many costs involved:
- The cost of ceasing blind-merged mining returns -- as stealing will kill a sidechain, all the fees from it that miners would be expected to earn for the next years are gone;
- The cost of Bitcoin price going down: If a steal is successful that will mean Drivechains are not safe, therefore Bitcoin is less useful, and miner credibility will also be hurt, which are likely to cause the Bitcoin price to go down, which in turn may kill the miners' businesses and savings;
- The cost of coordination -- assuming miners are just normal businesses, they just want to do their work and get paid, but stealing from a Drivechain will require coordination with other miners to conduct an immoral act in a way that has many pitfalls and is likely to be broken over the months;
- The cost of miners leaving your mining pool: when we talked about "miners" above we were actually talking about mining pools operators, so they must also consider the risk of miners migrating from their mining pool to others as they begin the process of stealing;
- The cost of community goodwill -- when participating in a steal operation, a miner will suffer a ton of backlash from the community. Even if the attempt fails at the end, the fact that it was attempted will contribute to growing concerns over exaggerated miners power over the Bitcoin ecosystem, which may end up causing the community to agree on a hard-fork to change the mining algorithm in the future, or to do something to increase participation of more entities in the mining process (such as development or cheapment of new ASICs), which have a chance of decreasing the profits of current miners.
Another point to take in consideration is that one may be inclined to think a newly-created sidechain or a sidechain with relatively low usage may be more easily stolen from, since the blind merged mining returns from it (point 1 above) are going to be small -- but the fact is also that a sidechain with small usage will also have less money to be stolen from, and since the other costs besides 1 are less elastic at the end it will not be worth stealing from these too.
All of the above consideration are valid only if miners are stealing from good sidechains. If there is a sidechain that is doing things wrong, scamming people, not being used at all, or is full of bugs, for example, that will be perceived as a bad sidechain, and then miners can and will safely steal from it and kill it, which will be perceived as a good thing by everybody.
What do we do if miners steal?
Paul Sztorc has suggested in the past that a user-activated soft-fork could prevent miners from stealing, i.e., most Bitcoin users and nodes issue a rule similar to this one to invalidate the inclusion of a faulty
WT^and thus cause any miner that includes it in a block to be relegated to their own Bitcoin fork that other nodes won't accept.This suggestion has made people think Drivechain is a sidechain solution backed by user-actived soft-forks for safety, which is very far from the truth. Drivechains must not and will not rely on this kind of soft-fork, although they are possible, as the coordination costs are too high and no one should ever expect these things to happen.
If even with all the incentives against them (see above) miners do still steal from a good sidechain that will mean the failure of the Drivechain experiment. It will very likely also mean the failure of the Bitcoin experiment too, as it will be proven that miners can coordinate to act maliciously over a prolonged period of time regardless of economic and social incentives, meaning they are probably in it just for attacking Bitcoin, backed by nation-states or something else, and therefore no Bitcoin transaction in the mainchain is to be expected to be safe ever again.
Why use this and not a full-blown trustless and open sidechain technology?
Because it is impossible.
If you ever heard someone saying "just use a sidechain", "do this in a sidechain" or anything like that, be aware that these people are either talking about "federated" sidechains (i.e., funds are kept in custody by a group of entities) or they are talking about Drivechain, or they are disillusioned and think it is possible to do sidechains in any other manner.
No, I mean a trustless 2-way peg with correctness of the withdrawals verified by the Bitcoin protocol!
That is not possible unless Bitcoin verifies all transactions that happen in all the sidechains, which would be akin to drastically increasing the blocksize and expanding the Bitcoin rules in tons of ways, i.e., a terrible idea that no one wants.
What about the Blockstream sidechains whitepaper?
Yes, that was a way to do it. The Drivechain hashrate escrow is a conceptually simpler way to achieve the same thing with improved incentives, less junk in the chain, more safety.
Isn't the hashrate escrow a very complex soft-fork?
Yes, but it is much simpler than SegWit. And, unlike SegWit, it doesn't force anything on users, i.e., it isn't a mandatory blocksize increase.
Why should we expect miners to care enough to participate in the voting mechanism?
Because it's in their own self-interest to do it, and it costs very little. Today over half of the miners mine RSK. It's not blind merged mining, it's a very convoluted process that requires them to run a RSK full node. For the Drivechain sidechains, an SPV node would be enough, or maybe just getting data from a block explorer API, so much much simpler.
What if I still don't like Drivechain even after reading this?
That is the entire point! You don't have to like it or use it as long as you're fine with other people using it. The hashrate escrow special addresses will not impact you at all, validation cost is minimal, and you get the benefit of people who want to use Drivechain migrating to their own sidechains and freeing up space for you in the mainchain. See also the point above about infighting.
See also
-
 @ 2e8970de:63345c7a
2025-03-31 19:08:11
@ 2e8970de:63345c7a
2025-03-31 19:08:11https://x.com/beatmastermatt/status/1906329250115858750
originally posted at https://stacker.news/items/930491
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16bitcoinddecentralizationIt is better to have multiple curator teams, with different vetting processes and release schedules for
bitcoindthan a single one."More eyes on code", "Contribute to Core", "Everybody should audit the code".
All these points repeated again and again fell to Earth on the day it was discovered that Bitcoin Core developers merged a variable name change from "blacklist" to "blocklist" without even discussing or acknowledging the fact that that innocent pull request opened by a sybil account was a social attack.
After a big lot of people manifested their dissatisfaction with that event on Twitter and on GitHub, most Core developers simply ignored everybody's concerns or even personally attacked people who were complaining.
The event has shown that:
1) Bitcoin Core ultimately rests on the hands of a couple maintainers and they decide what goes on the GitHub repository[^pr-merged-very-quickly] and the binary releases that will be downloaded by thousands; 2) Bitcoin Core is susceptible to social attacks; 2) "More eyes on code" don't matter, as these extra eyes can be ignored and dismissed.
Solution:
bitcoinddecentralizationIf usage was spread across 10 different
bitcoindflavors, the network would be much more resistant to social attacks to a single team.This has nothing to do with the question on if it is better to have multiple different Bitcoin node implementations or not, because here we're basically talking about the same software.
Multiple teams, each with their own release process, their own logo, some subtle changes, or perhaps no changes at all, just a different name for their
bitcoindflavor, and that's it.Every day or week or month or year, each flavor merges all changes from Bitcoin Core on their own fork. If there's anything suspicious or too leftist (or perhaps too rightist, in case there's a leftist
bitcoindflavor), maybe they will spot it and not merge.This way we keep the best of both worlds: all software development, bugfixes, improvements goes on Bitcoin Core, other flavors just copy. If there's some non-consensus change whose efficacy is debatable, one of the flavors will merge on their fork and test, and later others -- including Core -- can copy that too. Plus, we get resistant to attacks: in case there is an attack on Bitcoin Core, only 10% of the network would be compromised. the other flavors would be safe.
Run Bitcoin Knots
The first example of a
bitcoindsoftware that follows Bitcoin Core closely, adds some small changes, but has an independent vetting and release process is Bitcoin Knots, maintained by the incorruptible Luke DashJr.Next time you decide to run
bitcoind, run Bitcoin Knots instead and contribute tobitcoinddecentralization!
See also:
[^pr-merged-very-quickly]: See PR 20624, for example, a very complicated change that could be introducing bugs or be a deliberate attack, merged in 3 days without time for discussion.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28início
"Vocês vêem? Vêem a história? Vêem alguma coisa? Me parece que estou tentando lhes contar um sonho -- fazendo uma tentativa inútil, porque nenhum relato de sonho pode transmitir a sensação de sonho, aquela mistura de absurdo, surpresa e espanto numa excitação de revolta tentando se impôr, aquela noção de ser tomado pelo incompreensível que é da própria essência dos sonhos..."
Ele ficou em silêncio por alguns instantes.
"... Não, é impossível; é impossível transmitir a sensação viva de qualquer época determinada de nossa existência -- aquela que constitui a sua verdade, o seu significado, a sua essência sutil e contundente. É impossível. Vivemos, como sonhamos -- sozinhos..."
- Livros mencionados por Olavo de Carvalho
- Antiga homepage Olavo de Carvalho
- Bitcoin explicado de um jeito correto e inteligível
- Reclamações
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28On "zk-rollups" applied to Bitcoin
ZK rollups make no sense in bitcoin because there is no "cheap calldata". all data is already ~~cheap~~ expensive calldata.
There could be an onchain zk verification that allows succinct signatures maybe, but never a rollup.
What happens is: you can have one UTXO that contains multiple balances on it and in each transaction you can recreate that UTXOs but alter its state using a zk to compress all internal transactions that took place.
The blockchain must be aware of all these new things, so it is in no way "L2".
And you must have an entity responsible for that UTXO and for conjuring the state changes and zk proofs.
But on bitcoin you also must keep the data necessary to rebuild the proofs somewhere else, I'm not sure how can the third party responsible for that UTXO ensure that happens.
I think such a construct is similar to a credit card corporation: one central party upon which everybody depends, zero interoperability with external entities, every vendor must have an account on each credit card company to be able to charge customers, therefore it is not clear that such a thing is more desirable than solutions that are truly open and interoperable like Lightning, which may have its defects but at least fosters a much better environment, bringing together different conflicting parties, custodians, anyone.
-
 @ bcbb3e40:a494e501
2025-03-31 16:00:24
@ bcbb3e40:a494e501
2025-03-31 16:00:24|
 |
|:-:|
|WAJDA, Andrzej; Cenizas y diamantes, 1958|
|
|:-:|
|WAJDA, Andrzej; Cenizas y diamantes, 1958|Presentamos una nueva reseña cinematográfica, y en esta ocasión hemos elegido «Cenizas y diamantes», una película polaca del célebre y prolífico director Andrzej Wajda (1926-2016), estrenada en el año 1958. Se trata de uno de los grandes clásicos del cine polaco. El filme refleja una etapa dramática desde la perspectiva histórica para la nación polaca, como es el final de la Segunda Guerra Mundial, a raíz de la capitulación alemana del 8 de mayo de 1945. El contexto en el que se desarrolla se ambienta en la celebración del final de la guerra con el aplastante triunfo de la URSS, con las tropas soviéticas ocupando toda la Europa oriental, y en particular Polonia, que vive un momento de oscuridad e incertidumbre. El protagonista, Maciek Chełmicki (interpretado magistralmente por Zbigniew Cybulski (1927-1967), apodado el «James Dean polaco»), es un joven nacionalista polaco, de orientación anticomunista, que se ve implicado en un complot urdido para asesinar a un líder comunista local. Maciek opera desde la clandestinidad, bajo el grupo Armia Krajowa (AK), el Ejército Nacional polaco, una organización de resistencia, primero contra los alemanes y, posteriormente, contra los soviéticos. Durante el metraje, se plantea una dicotomía permanente entre la libertad entendida como la defensa de la soberanía de Polonia, desde posturas nacionalistas, y quienes consideran la ocupación soviética como algo positivo. Estas circunstancias atrapan al protagonista, que se ve envuelto en una espiral de violencia y traición.
Maciek Chełmicki, nuestro protagonista, cuenta con todas las características del héroe trágico, pues tiene en sus manos una serie de acciones que comprometen el futuro de un pueblo, que consiste en cumplir la misión que le ha sido encomendada, pero en su camino se cruza una joven, Krystyna, una joven camarera de un hotel de la que se enamora en ese mismo día. Este último hecho sirve de punto de partida para todas las dudas, dilemas y dicotomías a las que hacemos referencia. Hay un dilema moral evidente en un mundo en ruinas, devastado por la guerra, la muerte y el nihilismo. En este sentido Wajda nos muestra un lenguaje cinematográfico muy evidente, a través de una técnica expresionista muy depurada, con el uso del blanco y negro, los contrastes generados por las sombras y la atmósfera opresiva que transmite angustia, desesperación y vulnerabilidad de los protagonistas. Además también destilan una fuerte carga emocional, donde no están exentos elementos poéticos y un poderoso lirismo.
|
 |
|:-:|
|Maciek Chełmicki, el protagonista.|
|
|:-:|
|Maciek Chełmicki, el protagonista.|Hay elementos simbólicos que no podemos obviar, y que contribuyen a consolidar el análisis que venimos haciendo, como, por ejemplo, la estética del protagonista, con unas gafas oscuras, que actúan como una suerte de barrera frente al mundo que le rodea, como parte del anonimato tras el cual el joven Maciek vive de forma introspectiva su propio drama particular y el de toda una nación.
|
 |
|:-:|
|NITOGLIA, Curzio; En el mar de la nada: Metafísica y nihilismo a prueba en la posmodernidad; Hipérbola Janus, 2023|
|
|:-:|
|NITOGLIA, Curzio; En el mar de la nada: Metafísica y nihilismo a prueba en la posmodernidad; Hipérbola Janus, 2023|Hay una escena especialmente poderosa, y casi mítica, en la que los dos jóvenes protagonistas, Maciek y Krystina, se encuentran entre las ruinas de una Iglesia, en la que se destaca en primer plano, ocupando buena parte de la pantalla, la imagen de un Cristo invertido sobre un crucifijo, donde también se encuentran dos cuerpos colgados hacia abajo en una estampa que refleja la devastación moral y espiritual de toda una época. De hecho, la imagen del crucifijo invertido refleja el máximo punto de subversión y profanación de lo sagrado, y que en el caso concreto de la película viene a representar la destrucción del orden moral y de valores cristianos que la propia guerra ha provocado. Polonia es una nación profundamente católica, convertida al Cristianismo en el 966 a raíz de la conversión del príncipe Miecislao I, contribuyendo de manera decisiva a la formación de la identidad nacional polaca. El catolicismo siempre ha sido un medio de cohesión y defensa frente a las influencias extranjeras y la ocupación de terceros países, una constante en la historia del país, como el que ilustra la propia película con la URSS. En este sentido, la imagen de una Iglesia en ruinas, el lugar donde se encuentra representado el principio de lo sagrado e inviolable, supone una forma de perversión de todo principio de redención y salvación frente a la tragedia, y al mismo tiempo viene a significar que la Tradición ha sido abandonada y pervertida. En la misma línea, el protagonista, Maciek, se encuentra atrapado en una espiral de violencia a través de sus actos terroristas perpetrados contra la autoridad soviética que ocupa su país. Los dos cuerpos anónimos que cuelgan boca abajo, de forma grotesca, también participan de este caos y desequilibrio de un orden dislocado, son parte de la deshumanización y el nihilismo que todo lo impregna.
|
 |
|:-:|
|Maciek y Krystina en una iglesia en ruinas|
|
|:-:|
|Maciek y Krystina en una iglesia en ruinas|Como ya hemos mencionado, la película se encuentra plagada de paradojas y dicotomías, en las que nuestro protagonista, el joven rebelde e inconformista, debe elegir permanentemente, en unas decisiones que resultan trascendentales para su futuro y el de la propia nación. La figura femenina que irrumpe en su vida, y que representa un principio disruptivo que provoca una fractura interior y una crisis, le suscita una toma de conciencia de su propia situación y le fuerza a tomar un camino entre la «felicidad», del «amor», la «esperanza» y la «vida», que le permita superar la deriva nihilista y autodestructiva de la lucha clandestina, la cual le aboca a un destino trágico (que no vamos a desentrañar para no hacer spoiler). En relación al propio título de la película, «Cenizas y diamantes», basada en el poema del poeta y dramaturgo polaco Cyprian Norwid (1821-1883) y en la novela del autor, también polaco, Jerzy Andrzejewski (1909-1983), nos destaca la dualidad de los dos elementos que lo componen, y que definen el contraste entre el mundo sombrío y oscuro (Cenizas) y la esperanza y la luz que representa susodicha figura femenina (diamantes). La segunda alternativa parece un imposible, una quimera irrealizable que se pliega ante un Destino implacable, irreversible y cruel.
En consecuencia, y a la luz de los elementos expuestos, podemos decir que se nos presentan dilemas propios de la filosofía existencialista, que conoce su punto álgido en esos años, con autores como Jean Paul Sartre (1905-1980), Albert Camus (1913-1960), Karl Jaspers (1883-1969) o Martin Heidegger (1889-1976) entre otros. Respecto a éste último, a Heidegger, podemos encontrar algunas claves interesantes a través de su filosofía en relación al protagonista, a Maciek, especialmente a través de la idea del Dasein, a la idea de haber sido arrojado al mundo (Geworfenheit), y la manera tan extrema y visceral en la que vive susodicha condición. Todos aquellos elementos que dan sentido a la vida colectiva se encuentran decaídos o destruidos en su esencia más íntima, la Patria, la religión o la propia idea de Comunidad orgánica. De modo que el protagonista se ha visto «arrojado» frente a una situación o destino indeseado, en unas coyunturas totalmente desfavorables en las que no queda otra elección. Sus decisiones están permanentemente condicionadas por la circunstancia descrita y, por tanto, vive en un mundo donde no controla nada, en lugar de ser sujeto es un mero objeto transportado por esas circunstancias ajenas a su voluntad. Sin embargo, y en coherencia con el Dasein heideggeriano, vemos como Maciek, a raíz de conocer a Krystyna, comienza a experimentar una catarsis interior, que muestra por momentos el deseo de superar ese «ser arrojado al mundo contra tu voluntad», trascendiendo esa condición absurda e irracional de unas decisiones enajenadas de su voluntad para dotar de una significación y un sentido la propia existencia.
|
 |
|:-:|
|Andrzej Wajda, el director de la película.|
|
|:-:|
|Andrzej Wajda, el director de la película.|Otro elemento característico de la filosofía heideggeriana lo podemos encontrar en la «angustia» (angst) a través de la ausencia de un sentido y fundamento último que justifique la existencia del protagonista. Es una angustia en a que el Dasein se enfrenta a la «nada», a ese vacío existencial que hace inútil toda la lucha que Maciek lleva a cabo en la clandestinidad, con asesinatos y actos de terrorismo que pretenden salvaguardar algo que ya no existe, y que simboliza muy bien la Iglesia en ruinas con sus símbolos religiosos invertidos de la que hablábamos con anterioridad. Recuerda un poco a esa dicotomía que se plantea entre ser conservador o reaccionario frente a una realidad como la del propio presente, en la que los valores tradicionales han sido totalmente destruidos, y más que conservar se impone la reacción para volver a construir de la nada.
|
 |
|:-:|
|Hipérbola Janus; Textos para la Tradición en tiempos del oscurecimiento: Artículos publicados entre 2014 y 2019 en hiperbolajanus.com; Hipérbola Janus, 2019|
|
|:-:|
|Hipérbola Janus; Textos para la Tradición en tiempos del oscurecimiento: Artículos publicados entre 2014 y 2019 en hiperbolajanus.com; Hipérbola Janus, 2019|Todas las dudas que asaltan al protagonista se ven incrementadas en el momento decisivo, cuando se dispone a dar muerte al líder comunista. Se produce una tensión interna en Maciek, que se encuentra ligado a la joven que ha conocido ese día, y en ella es donde encuentra ese leve destello de humanidad. Esa circunstancia le hace replantearse por un instante el cumplimiento de su misión, pero es un dilema que no tiene salida, y por ello le asalta nuevamente la angustia frente a esa «nada», ese mundo vacío e incomprensible que trasciende el marco de sus propias elecciones.
Uno de los conceptos centrales de Heidegger en Ser y tiempo es el Sein-zum-Tode (ser-para-la-muerte), la idea de que la muerte es la posibilidad más propia y definitiva del Dasein, y que enfrentarla auténticamente permite vivir de manera más plena. Y es que el protagonista se encuentra permanentemente sobre esa frontera entre la vida y la muerte, que afronta con todas sus consecuencias, conscientemente, y la acepta. Esta actitud podría leerse como una forma de Dasein inauténtico, una huida del ser-para-la-muerte mediante la distracción (das Man, el «se» impersonal). Sin embargo, su decisión de cumplir la misión sugiere un enfrentamiento final con esa posibilidad. Otro aspecto que podemos conectar con el pensamiento heideggeriano es la autenticidad o inautenticidad de la vida del protagonista. En relación a la inautenticidad vemos como al principio sigue las órdenes de sus superiores en la organización sin cuestionarlas, lo cual implica un comportamiento inequívocamente alienante. Respecto a aquello que resulta auténtico de su existencia son sus relaciones con Krystyna, que supone imponer su propia voluntad y decisión, mostrando un Dasein que asume su libertad.
|
 |
|:-:|
|Escena de la película.|
|
|:-:|
|Escena de la película.|Otros aspectos más generales de la filosofía existencialista redundan sobre estos mismos aspectos, con la elección entre la libertad absoluta y la condena inevitable. La idea del hombre condenado a actuar, a una elección continua, aún cuando el hombre no es dueño de su destino, o las consecuencias de tales acciones son absurdas, irracionales e incomprensibles. El propio absurdo de la existencia frente al vacío y la ausencia de principios sólidos en los que cimentar la vida, no solo en sus aspectos cotidianos más básicos, sino en aquellos más profundos de la existencia. La soledad y la propia fatalidad frente a un Destino que, como ya hemos apuntado anteriormente, parece imponerse de manera irrevocable, y podríamos decir que brutalmente, al individuo aislado, incapaz de asirse en una guía, en unos valores que le permitan remontar la situación.
En términos generales «Cenizas y diamantes», además de ser una película de gran calidad en sus aspectos técnicos, en su fotografía, en la configuración de sus escenas y en el propio desarrollo argumental, bajo un guión espléndidamente ejecutado a lo largo de sus 98 minutos de duración, también nos invita a una reflexión profunda sobre la condición humana y la propia Modernidad. Y es algo que vemos en nuestros días, con las consecuencias de un pensamiento débil, con la promoción del individualismo, el hedonismo y lo efímero. La ausencia de estructuras sólidas, la subversión de toda forma de autoridad y jerarquía tradicionales. Paradójicamente, el mundo actual tiende a formas de poder y autoridad mucho más invasivas y coercitivas, tanto a nivel individual como colectivo, pero en la misma línea abstracta e impersonal que nos describe la película, abocándonos a la alienación y la inautenticidad de nuestras propias vidas. Y como Maciek, también nosotros, vivimos en un mundo dominado por la incertidumbre y la desesperanza, en el que el globalismo y sus perversas ideologías deshumanizantes actúan por doquier.
|
 |
|:-:|
|Carátula original de la película en polaco.|
|
|:-:|
|Carátula original de la película en polaco.|
Artículo original: Hipérbola Janus, Reseña de «Cenizas y Diamantes» (Andrzej Wajda, 1958) (TOR), 31/Mar/2025
-
 @ bcbb3e40:a494e501
2025-03-31 15:41:53
@ bcbb3e40:a494e501
2025-03-31 15:41:53El 7 de febrero de 2025, Donald Trump firmó una orden ejecutiva que establecía una «Oficina de la Fe» en la Casa Blanca, dirigida por su asesora espiritual Paula White-Cain, la pastora de esa «teología de la prosperidad» (prosperity theology) que predica el «Evangelio de la salud y la riqueza» (health and wealth gospel^1). Investida de su nueva función, la reverenda pastora dijo: «Tengo la autoridad para declarar a la Casa Blanca un lugar santo. Es mi presencia la que la santifica»[^2]. Los siete rabinos del «Sanedrín Naciente» —la corte suprema que guiará a Israel cuando se reconstruya el Templo de Jerusalén— enviaron conmovedoras felicitaciones al presidente Trump por el establecimiento de esta Oficina. «Expresamos nuestra sincera gratitud —se lee en el mensaje oficial enviado a Trump desde el Monte Sión— por llevar la fe a la vanguardia de la cultura estadounidense y mundial mediante el establecimiento de la Oficina de la Fe en la Casa Blanca. Su reconocimiento de la importancia de la religión en la vida pública es un paso hacia la restauración de los valores morales y del liderazgo espiritual en el mundo[^3]. La carta del «Sanedrín Naciente», que augura el éxito a la «misión divina» del presidente estadounidense, reproduce las dos caras de una «moneda del Templo», acuñada en 2017 para celebrar el traslado de la embajada estadounidense a Jerusalén y, simultáneamente, el centenario de la Declaración Balfour. En el anverso se ven los perfiles de Donald Trump y Ciro el Grande, a quien la tradición judía atribuye la reconstrucción del templo destruido por los babilonios, con la inscripción (en hebreo e inglés) «Cyrus —Balfour— Trump Declaration 1917-2017»; en el reverso está la imagen del Templo de Jerusalén[^4]. Otra moneda, que lleva los perfiles de Trump y Ciro en el anverso y los de Trump y Netanyahu en el reverso, fue acuñada en 2018 para celebrar el septuagésimo aniversario de la independencia del «Estado de Israel»; se observa dos inscripciones en hebreo e inglés: «Y Él me encargó construirle una casa en Jerusalén» y «Guerra de los Hijos de la Luz contra los Hijos de las Tinieblas».
El tema de la «guerra de los Hijos de la Luz contra los Hijos de las Tinieblas» ha tenido una difusión particular en el imaginario y la propaganda trumpista. El 7 de junio de 2020, monseñor Carlo Maria Viganò, ex nuncio de la Santa Sede en los Estados Unidos, escribió una carta al presidente Donald Trump que comenzaba así: «Estamos asistiendo en los últimos meses a la formación de dos bandos, que los definiría bíblicos: los hijos de la luz y los hijos de las tinieblas»[^5]. El 1 de enero de 2021, el agitprop estadounidense Steve Bannon declaró en una entrevista con Monseñor Viganò: «Esta es una batalla de época entre los hijos de la Luz y los hijos de las Tinieblas»[^6].
Son numerosos los judíos sionistas que están en el círculo del presidente Trump: además de su hija Ivanka (convertida en 2009) y su yerno Jared Kushner (entonces Consejero Anciano del Presidente), el 19 de noviembre de 2024 el «The Jerusalem Post»[^7] publicó una lista de los más influyentes: Stephen Miller, subdirector del staff de la Casa Blanca y consejero de Seguridad Nacional de Estados Unidos; David Melech Friedman, a quien en 2016 Trump nombró embajador en Israel; el multimillonario «filántropo» Steven Charles Witkoff, enviado especial de Estados Unidos a Oriente Medio; Miriam Adelson, directora del periódico «Israel Hayom», clasificada por Bloomberg Billionaires como la quinta mujer más rica del mundo (con un patrimonio neto de 32,400 millones de dólares), financiadora de iniciativas políticas conservadoras en Estados Unidos e Israel; el banquero Boris Epshteyn, consejero estratégico de la campaña presidencial de Trump en 2020; Howard Williams Lutnick, presidente de la Cantor Fitzgerald del Grupo BGC, financista de las campañas presidenciales de Donald Trump en 2020 y 2024, ahora secretario de Comercio; la modelo Elizabeth Pipko, portavoz nacional del Partido Republicano y creadora de un «museo interactivo virtual» sobre la «Shoah» como parte del proyecto de Lest People Forget, cuyo objetivo es combatir el «antisemitismo» y la «negacionismo»; Lee Michael Zeldin, miembro republicano de la Cámara de Representantes por el estado de Nueva York del 2015 al 2023 y actualmente administrador de la EPA (Environmental Protection Agency); la columnista Laura Elizabeth Loomer, «orgullosamente islamófoba», activa patrocinadora de Trump en la campaña para las elecciones presidenciales de 2024; Sidney Ferris Rosenberg, influyente presentador de radio y periodista deportivo; William Owen Scharf, Asistente del Presidente y secretario del personal de la Casa Blanca; Marc Jeffrey Rowan, «filántropo» con un patrimonio neto valorado por Forbes en ocho mil ochocientos millones de dólares.
Además de estos, cabe mencionar al popular presentador de radio Mark Levin quien, en diciembre de 2019, durante la celebración de la fiesta de Janucá en la Casa Blanca, saludó a Donald Trump como «el primer presidente judío de los Estados Unidos»[^8]. Según un funcionario de alto nivel de la Casa Blanca, Donald Trump se convirtió al judaísmo dos años antes en la sinagoga de la secta Jabad Lubavitch en la ciudad de Nueva York. David Elias Goldberg, miembro del Jewish Center of Antisemitic Study, también entrevistó al funcionario, para quien «Trump fue “instado” por su hija Ivanka y su yerno Jared Kushner para abrazar la fe. Inicialmente, Trump se habría mostrado reacio, considerando que esto podría enfriar el apoyo del electorado evangélico». Luego, informa «Israel Today News», «cambió de opinión y se convirtió oficialmente a principios de 2017. La ceremonia se llevó a cabo en privado y se guardó celosamente durante casi dos años»[^9]. Pero ya en septiembre de 2015, el rabino millonario Kirt Schneider, invitado a la Trump Tower de Nueva York, había impuesto sus manos sobre la cabeza de Donald Trump y lo había bendecido en hebreo e inglés, declarando: «Las únicas dos naciones que tienen una relación privilegiada con Dios son Israel y los Estados Unidos de América»[^10].
El 7 de octubre de 2024, en el aniversario de la operación de Hamas «Diluvio de Al-Aqsa», Trump fue acompañado por un «superviviente de la Shoah» a la tumba de Menachem Mendel Schneerson, séptimo y último Rabino de los Hasidim de la secta Jabad Lubavitch, que en 1991 declaró a sus seguidores: «He hecho todo lo posible para provocar el arribo del Mesías, ahora les paso a ustedes esta misión; hagan todo lo que puedan para que Él venga»^11. En relación al evento mesiánico, el eminente rabino Yekutiel Fish atribuyó una misión decisiva a Trump: «Todo el mundo está centrado en Gaza, pero esa es solo una parte de la agenda del fin de los tiempos, que tiene a los judíos viviendo en las fronteras profetizadas de Israel; la Torá incluye explícitamente a Gaza. Lo que Trump está haciendo es limpiar Gaza de todos los odiadores de Israel. No podrán estar en Israel después de la venida del Mesías. (...) Esto incluirá a Gaza, la mitad del Líbano y gran parte de Jordania. Y vemos que casi lo hemos logrado. Siria cayó. Líbano está medio destruido. Gaza está destrozada. El escenario está casi listo para el Mesías. Pero, ¿cómo pueden los palestinos estar aquí cuando vayamos a recibir al Mesías? El Mesías necesita que alguien se ocupe de esto, y en este caso, es Donald Trump. Trump está simplemente llevando a cabo las tareas finales necesarias antes de que el Mesías sea revelado»[^12].
Esta inspiración escatológica está presente en las palabras de Pete Brian Hegseth, el pintoresco exponente del «Reconstruccionismo Cristiano»[^13] a quien Trump nombró secretario de Defensa. En un discurso pronunciado en 2019 en el Hotel Rey David de Jerusalén, con motivo de la conferencia anual del canal Arutz Sheva (Israel National News), Hegseth enalteció el «vínculo eterno» entre Israel y Estados Unidos, y enumeró los «milagros» que atestiguan el «apoyo divino» a la causa sionista, el último de los cuales será la reconstrucción del Templo judío en la zona donde actualmente se encuentra la mezquita de al-Aqsa: «La dignidad de capital adquirida por Jerusalén —dijo— fue un milagro, y no hay razón por la cual no sea posible el milagro de la restauración del Templo en el Monte del Templo».[^14]
Es conocido que el fundamentalismo evangélico pro-sionista[^15] comparte con el judaísmo la creencia en que la construcción del tercer Templo de Jerusalén marcará el comienzo de la era mesiánica; cuando la administración Trump trasladó la embajada de Estados Unidos a Jerusalén en 2017, Laurie Cardoza-Moore, exponente del evangelismo sionista, saludó así la «obediencia de Trump a la Palabra de Dios» en «Haaretz»: «Al establecer la Embajada en Jerusalén, el presidente Donald Trump está implementando una de las iniciativas históricas de dimensión bíblica en su presidencia. Al igual que muchos judíos en Israel y en todo el mundo, los cristianos reconocen el vínculo de los judíos con la Biblia a través del nombre de Jerusalén como la capital del antiguo Israel, así como el sitio del Primer y Segundo Templos. Según los profetas Ezequiel, Isaías y el apóstol Juan del Nuevo Testamento, todos los israelíes esperan la reconstrucción del Tercer Templo»[^16]. El 22 de mayo del mismo año, Donald Trump, acompañado de su esposa Melania, de su hija Ivanka y su yerno Jared Kushner, fue el primer presidente de los Estados Unidos en ejercicio en acudir al Muro de las Lamentaciones, anexionado ilegalmente a la entidad sionista.
En 2019, la administración Trump confirmó la posición de Estados Unidos al enviar en visita oficial para Jerusalén a Mike Pompeo, un secretario de Estado que —ironía de la Historia— lleva el mismo nombre del general romano que asaltó la ciudad en el año 63 a.C. «Por primera vez en la historia, un secretario de Estado norteamericano visitó la Ciudad Vieja de Jerusalén en compañía de un alto político israelí. Fue una visita histórica que reforzó las expectativas israelíes y constituyó un reconocimiento tácito de la soberanía israelí sobre el sitio del Monte del Templo y la Explanada de las Mezquitas. (…) Mike Pompeo, acompañado por el primer ministro Benjamin Netanyahu y el embajador de Estados Unidos en Israel, David Friedman, también visitó el túnel del Muro de las Lamentaciones y la sinagoga ubicada bajo tierra, en el presunto lugar del santuario del Templo[^17], donde se le mostró una maqueta del futuro Templo[^18]. En el transcurso de una entrevista concedida durante la fiesta del Purim (que celebra el exterminio de la clase política persa, ocurrido hace 2500 años), el secretario de Estado insinuó que «el presidente Donald Trump puede haber sido enviado por Dios para salvar al pueblo judío y que confiaba en que aquí el Señor estaba obrando»[^19].
Como observa Daniele Perra, en este mismo número de «Eurasia», el «mito movilizador» del Tercer Templo, atribuible a los «mitos teológicos» señalados por Roger Garaudy como mitos fundadores de la entidad sionista, «atribuye al judaísmo una especie de función sociológica de transmisión y proyección del conflicto palestino-israelí hacia el resto del mundo y confiere una inspiración apocalíptica al momento geopolítico actual».
|Info|| |:-|:-| |Autor| Claudio Mutti | |Fuente| I "Figli della Luce" alla Casa Bianca | |Fecha| 8/Mar/2025 | |Traducción| Francisco de la Torre |
[^2]: The White House, President Trump announces appointments to the White House Faith Office https://www.whitehouse.gov,, 7 de febrero de 2025; Trump establece la Oficina de la Fe con una foto de «La Última Cena» | Fue dirigida por la controvertida predicadora Paula White, https://www.tgcom24.mediaset.it, 10 de febrero de 2025.
[^3]: «We extend our heartfelt gratitude for bringing faith to the forefront of American and global culture through the establishment of the Faith Office in the White House. Your recognition of the importance of religion in public life is a step toward restoring moral values and spiritual leadership in the world» (Letter from the Nascent Sanhedrin to President Donald J. Trump, Jerusalem, Wednesday, February 12, 2025).
[^4]: Israeli group mints Trump coin to honor Jerusalem recognition, «The Times of Israel», https://www.timesofisrael.com, 28-2-2018.
[^5]: Mons. Viganò — Siamo nella battaglia tra figli della luce e figli delle tenebre, https://www.italiador.com, 7-6-2020
[^6]: TRANSCRIPT: Steve Bannon’s ‘War Room’ interview with Abp. Viganò, lifesitenews.com, 4-1-2021. Sulle origini e sulla fortuna di questo tema cfr. C. Mutti, Le sètte dell’Occidente, «Eurasia», 2/2021, pp. 12-15. (https://www.eurasia-rivista.com/las-sectas-de-occidente/)
[^7]: Luke Tress, The who’s who of Jews in Trump’s inner circle?, «The Jerusalem Post», https://www.jpost.com, 19-11-2024.
[^8]: Radio Talk Show Host Mark Levin Calls President Trump «the First Jewish President of the United States», https://www.c-span.org, 11-12-2019.
[^9]: «However, he had a change of heart and officially converted in early 2017. The ceremony was held in private, and closely guarded for nearly two years» (Donald Trump converted to Judaism two years ago, according to White House official, https://israeltodaynews.blogspot.com/2019/02).
[^10]: «El rabino Kirt Schneider (...) es un millonario judío, una figura televisiva de los “judíos mesiánicos”. Sus emisiones televisivas semanales son emitidas por más de treinta canales cristianos en unos doscientos países; entre ellos, los canales “Yes” y “Hot” en Israel. Solo en Estados Unidos, sus emisiones atraen a 1.600.000 telespectadores cada semana. Kirt Schneider dirige un imperio de telecomunicaciones que tiene un millón y medio de seguidores en Facebook, X (antes Twitter) y YouTube» (Pierre-Antoine Plaquevent — Youssef Hindi, El milenarismo teopolítico de Israel, Edizioni all'insegna del Veltro, Parma 2025, p. 31).
[^12]: «Everyone is focused on Gaza, but that is only one part of the end-of-days agenda, which has the Jews living in Israel’s prophesied borders. The Torah explicitly includes Gaza. What Trump is doing is cleaning out Gaza of all the haters of Israel. They cannot be in Israel after the Messiah comes. (…) This will include Gaza, half of Lebanon, and much of Jordan. And we see that we are almost there. Syria fell. Lebanon is half gone. Gaza is ripped up. The stage is nearly set for Messiah. But how can the Palestinians be here when we go to greet the Messiah? The Messiah needs someone to take care of this, and in this case, it is Donald Trump. Trump is merely carrying out the final tasks needed before Messiah is revealed» (Adam Eliyahu Berkowitz, Trump’s Gaza Plan is «The Final task before Messiah», https://israel365news.com, 5-2-2025).
[^13]: «A day after Hegseth was announced for the Cabinet position, Brooks Potteiger, a pastor within the Communion of Reformed Evangelical Churches (CREC), posted on X that Hegseth is a member of the church in good standing. The CREC, a denomination of Christian Reconstructionism, is considered by some academics to be an extremist, Christian supremacist movement» (Shannon Bond e altri, What’s behind defense secretary pick Hegseth’s war on ‘woke’, https://www.npr.org, 14-11-2024.
[^14]: «The decoration of Jerusalem as a capital was a miracle, and there is no reason why the miracle of the re-establishment of Temple on the Temple Mount is not possible» (Pete Hegseth at Arutz Sheva Conference, youtube.com). Cfr. Daniele Perra, Paleotrumpismo, neotrumpismo e post-trumpismo, in: AA. VV., Trumpismo, Cinabro Edizioni, Roma 2025, pp. 22-23.
[^15]: Pierre-Antoine Plaquevent — Youssef Hindi, El milenarismo teopolítico de Israel, cit., págs. 82 a 96.
[^16]: «We American Christians Welcome Trump’s Obedience to God’s Word on Jerusalem», «Haaretz», 6-12-2017.
[^17]: Pierre-Antoine Plaquevent — Youssef Hindi, El milenarismo teopolítico de Israel, cit., pág. 97.
[^18]: Pompeo en visite historique au mur Occidental aux côtés de Netanyahu et Friedman, «The Times of Israel», https://fr.timesofisrael.com, 21-3-2019.
[^19]: Pompeo says Trump may have been sent by God to save Jews from Iran, «The Times of Israel», 22-3-2019.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28The problem with ION
ION is a DID method based on a thing called "Sidetree".
I can't say for sure what is the problem with ION, because I don't understand the design, even though I have read all I could and asked everybody I knew. All available information only touches on the high-level aspects of it (and of course its amazing wonders) and no one has ever bothered to explain the details. I've also asked the main designer of the protocol, Daniel Buchner, but he may have thought I was trolling him on Twitter and refused to answer, instead pointing me to an incomplete spec on the Decentralized Identity Foundation website that I had already read before. I even tried to join the DIF as a member so I could join their closed community calls and hear what they say, maybe eventually ask a question, so I could understand it, but my entrance was ignored, then after many months and a nudge from another member I was told I had to do a KYC process to be admitted, which I refused.
One thing I know is:
- ION is supposed to provide a way to rotate keys seamlessly and automatically without losing the main identity (and the ION proponents also claim there are no "master" keys because these can also be rotated).
- ION is also not a blockchain, i.e. it doesn't have a deterministic consensus mechanism and it is decentralized, i.e. anyone can publish data to it, doesn't have to be a single central server, there may be holes in the available data and the protocol doesn't treat that as a problem.
- From all we know about years of attempts to scale Bitcoins and develop offchain protocols it is clear that you can't solve the double-spend problem without a central authority or a kind of blockchain (i.e. a decentralized system with deterministic consensus).
- Rotating keys also suffer from the double-spend problem: whenever you rotate a key it is as if it was "spent", you aren't supposed to be able to use it again.
The logic conclusion of the 4 assumptions above is that ION is flawed: it can't provide the key rotation it says it can if it is not a blockchain.
See also
-
 @ 78b3c1ed:5033eea9
2025-04-27 01:48:48
@ 78b3c1ed:5033eea9
2025-04-27 01:48:48※スポットライトから移植した古い記事です。参考程度に。
これを参考にしてUmbrelのBitcoin Nodeをカスタムsignetノードにする。 以下メモ書きご容赦。備忘録程度に書き留めました。
メインネットとは共存できない。Bitcoinに依存する全てのアプリを削除しなければならない。よって実験機に導入すべき。
<手順>
1.Umbrel Bitcoin Nodeアプリのadvance settingでsignetを選択。
2.CLI appスクリプトでbitcoinを止める。
cd umbrel/scripts ./app stop bitcoin3.bitcoin.conf, umbrel-bitcoin.conf以外を削除ディレクトリの場所は ~/umbrel/app-data/bitcoin/data/bitcoin4.umbrel-bitcoin.confをsu権限で編集。末尾にsignetchallengeを追加。 ``` [signet] bind=0.0.0.0:8333 bind=10.21.21.8:8334=onion51,21,<公開鍵>,51,ae
signetchallenge=5121<公開鍵>51ae
5.appスクリプトでbitcoinを開始。cd ~/umbrel/scripts ./app start bitcoin ``` 6.適当にディレクトリを作りgithubからbitcoindのソースをクローン。7.bitcoindのバイナリをダウンロード、bitcoin-cliおよびbitcoin-utilを~/.local/binに置く。6.のソースからビルドしても良い。ビルド方法は自分で調べて。
8.bitcondにマイニング用のウォレットを作成 ``` alias bcli='docker exec -it bitcoin_bitcoind_1 bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>'
ウォレットを作る。
bcli createwallet "mining" false true "" false false
秘密鍵をインポート
bcli importprivkey "<秘密鍵>"
RPCパスワードは以下で確認cat ~/umbrel/.env | grep BITCOIN_RPC_PASS9.ソースにあるbitcoin/contrib/signet/minerスクリプトを使ってマイニングcd <ダウンロードしたディレクトリ>/bitcoin/contrib/signet難易度の算出
./miner \ --cli="bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>" calibrate \ --grind-cmd="bitcoin-util grind" --seconds 30 ★私の環境で30秒指定したら nbits=1d4271e7 と算出された。実際にこれで動かすと2分30になるけど...
ジェネシスブロック生成
./miner \ --cli="bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>" generate \ --address <ビットコインアドレス> \ --grind-cmd="bitcoin-util grind" --nbits=1d4271e7 \ --set-block-time=$(date +%s)
継続的にマイニング
./miner \ --cli="bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>" generate \ --address <ビットコインアドレス> \ --grind-cmd="bitcoin-util grind" --nbits=1d4271e7 \ --ongoing ``` ここまでやればカスタムsignetでビットコインノードが稼働する。
-
 @ 78b3c1ed:5033eea9
2025-04-27 01:42:48
@ 78b3c1ed:5033eea9
2025-04-27 01:42:48・ThunderHubで焼いたマカロンがlncli printmacaroonでどう見えるか確認した。
ThunderHub macaroon permissions
get invoices invoices:read create invoices invoices:write get payments offchain:read pay invoices offchain:write get chain transactions onchain:read send to chain address onchain:write create chain address address:write get wallet info info:read stop daemon info:write この結果によれば、offchain:wirteとonchain:writeの権限がなければそのマカロンを使うクライアントは勝手にBTCを送金することができない。 info:writeがなければ勝手にLNDを止めたりすることができない。
・lncli printmacaroonでデフォルトで作られるmacaroonのpermissionsを調べてみた。 admin.macaroon
{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "info:read", "info:write", "invoices:read", "invoices:write", "macaroon:generate", "macaroon:read", "macaroon:write", "message:read", "message:write", "offchain:read", "offchain:write", "onchain:read", "onchain:write", "peers:read", "peers:write", "signer:generate", "signer:read" ], "caveats": null }chainnotifier.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "onchain:read" ], "caveats": null }invoice.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "invoices:read", "invoices:write", "onchain:read" ], "caveats": null }invoices.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "invoices:read", "invoices:write" ], "caveats": null }readonly.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "info:read", "invoices:read", "macaroon:read", "message:read", "offchain:read", "onchain:read", "peers:read", "signer:read" ], "caveats": null }router.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "offchain:read", "offchain:write" ], "caveats": null }signer.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "signer:generate", "signer:read" ], "caveats": null }walletkit.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "onchain:read", "onchain:write" ], "caveats": null }・lncli listpermissions コマンドですべての RPC メソッド URI と、それらを呼び出すために必要なマカロン権限を一覧表示できる。 LND v0.18.5-betaでやると1344行ほどのJSONができる。 AddInvoiceだとinvoice:writeのpermissionを持つmacaroonを使えばインボイスを作れるようだ。
"/lnrpc.Lightning/AddInvoice": { "permissions": [ { "entity": "invoices", "action": "write" } ] },lncli listpermissionsからentityとactionを抜き出してみた。 ``` "entity": "address", "entity": "info", "entity": "invoices", "entity": "macaroon", "entity": "message", "entity": "offchain", "entity": "onchain", "entity": "peers", "entity": "signer","action": "generate" "action": "read" "action": "write"
lncli とjqを組み合わせると例えば以下コマンドでinvoices:writeを必要とするRPCの一覧を表示できる。 invoices:writeだとAddInvoiceの他にホドルインボイス作成でも使ってるようだlncli listpermissions | jq -r '.method_permissions | to_entries[] | select(.value.permissions[] | select(.entity == "invoices" and .action == "write")) | .key'/invoicesrpc.Invoices/AddHoldInvoice /invoicesrpc.Invoices/CancelInvoice /invoicesrpc.Invoices/HtlcModifier /invoicesrpc.Invoices/LookupInvoiceV2 /invoicesrpc.Invoices/SettleInvoice /lnrpc.Lightning/AddInvoiceinvoices:readだと以下となる。/invoicesrpc.Invoices/SubscribeSingleInvoice /lnrpc.Lightning/ListInvoices /lnrpc.Lightning/LookupInvoice /lnrpc.Lightning/SubscribeInvoicesLNの主だった機能のRPCはoffchainが必要ぽいので抜き出してみた。 offchain:write チャネルの開閉、ペイメントの送信までやってるみたい。 デフォルトのmacaroonでoffchain:writeを持ってるのはadminとrouterの2つだけ。openchannel,closechannelはonchain:writeのpermissionも必要なようだ。/autopilotrpc.Autopilot/ModifyStatus /autopilotrpc.Autopilot/SetScores /lnrpc.Lightning/AbandonChannel /lnrpc.Lightning/BatchOpenChannel /lnrpc.Lightning/ChannelAcceptor /lnrpc.Lightning/CloseChannel /lnrpc.Lightning/DeleteAllPayments /lnrpc.Lightning/DeletePayment /lnrpc.Lightning/FundingStateStep /lnrpc.Lightning/OpenChannel /lnrpc.Lightning/OpenChannelSync /lnrpc.Lightning/RestoreChannelBackups /lnrpc.Lightning/SendCustomMessage /lnrpc.Lightning/SendPayment /lnrpc.Lightning/SendPaymentSync /lnrpc.Lightning/SendToRoute /lnrpc.Lightning/SendToRouteSync /lnrpc.Lightning/UpdateChannelPolicy /routerrpc.Router/HtlcInterceptor /routerrpc.Router/ResetMissionControl /routerrpc.Router/SendPayment /routerrpc.Router/SendPaymentV2 /routerrpc.Router/SendToRoute /routerrpc.Router/SendToRouteV2 /routerrpc.Router/SetMissionControlConfig /routerrpc.Router/UpdateChanStatus /routerrpc.Router/XAddLocalChanAliases /routerrpc.Router/XDeleteLocalChanAliases /routerrpc.Router/XImportMissionControl /wtclientrpc.WatchtowerClient/AddTower /wtclientrpc.WatchtowerClient/DeactivateTower /wtclientrpc.WatchtowerClient/RemoveTower /wtclientrpc.WatchtowerClient/TerminateSession"/lnrpc.Lightning/OpenChannel": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] },offchain:read readの方はチャネルやインボイスの状態を確認するためのpermissionのようだ。/lnrpc.Lightning/ChannelBalance /lnrpc.Lightning/ClosedChannels /lnrpc.Lightning/DecodePayReq /lnrpc.Lightning/ExportAllChannelBackups /lnrpc.Lightning/ExportChannelBackup /lnrpc.Lightning/FeeReport /lnrpc.Lightning/ForwardingHistory /lnrpc.Lightning/GetDebugInfo /lnrpc.Lightning/ListAliases /lnrpc.Lightning/ListChannels /lnrpc.Lightning/ListPayments /lnrpc.Lightning/LookupHtlcResolution /lnrpc.Lightning/PendingChannels /lnrpc.Lightning/SubscribeChannelBackups /lnrpc.Lightning/SubscribeChannelEvents /lnrpc.Lightning/SubscribeCustomMessages /lnrpc.Lightning/VerifyChanBackup /routerrpc.Router/BuildRoute /routerrpc.Router/EstimateRouteFee /routerrpc.Router/GetMissionControlConfig /routerrpc.Router/QueryMissionControl /routerrpc.Router/QueryProbability /routerrpc.Router/SubscribeHtlcEvents /routerrpc.Router/TrackPayment /routerrpc.Router/TrackPaymentV2 /routerrpc.Router/TrackPayments /wtclientrpc.WatchtowerClient/GetTowerInfo /wtclientrpc.WatchtowerClient/ListTowers /wtclientrpc.WatchtowerClient/Policy /wtclientrpc.WatchtowerClient/Stats・おまけ1 RPCメソッド名にopenを含む要素を抽出するコマンドlncli listpermissions | jq '.method_permissions | to_entries[] | select(.key | test("open"; "i"))'{ "key": "/lnrpc.Lightning/BatchOpenChannel", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } } { "key": "/lnrpc.Lightning/OpenChannel", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } } { "key": "/lnrpc.Lightning/OpenChannelSync", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } }・おまけ2 thunderhubで作ったmacaroonはテキストで出力されコピペして使うもので、macaroonファイルになってない。 HEXをmacaroonファイルにするには以下コマンドでできる。HEXをコピペして置換する。またYOURSの箇所を自分でわかりやすい名称に置換すると良い。echo -n "HEX" | xxd -r -p > YOURS.macaroonthunderhubで"Create Invoices, Get Invoices, Get Wallet Info, Get Payments, Pay Invoices"をチェックして作ったmacaroonのpermissionsは以下となる。{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "info:read", "invoices:read", "invoices:write", "offchain:read", "offchain:write" ], "caveats": null } ``` offchain:writeはあるがonchain:writeがないのでチャネル開閉はできないはず。 -
 @ 9bcc5462:eb501d90
2025-04-04 16:02:14
@ 9bcc5462:eb501d90
2025-04-04 16:02:14The story you are about to read is one hundred percent true. It is also my first encounter with a supernatural force.
It was the summer of 2003 and I was visiting my auntie in Nashville as a 16-year-old, pimply-faced teenager. My younger cousins, Alex, Mikey, and Tony were also there. One afternoon, they were all sitting bored outside in the blazing heat, sheltered under the tree on the front lawn. It was a comical sight really, all of them sprawled out lifeless and silent, eaten alive by the unforgiving mosquitos. I ducked inside and asked my aunt if it was okay to borrow her RAV4 to take them to play basketball nearby at Pitts Park. Despite not having a license she handed me the keys and when I went outside to tell the boys we were going to shoot hoops, you’d have thought I said I was taking them to Disney World!
Off we went up and down the rollercoaster-like hills of Tennessee. Yes, I was speeding, and no, we were not wearing seatbelts. (Remember, sixteen, acne, angst, etc.) We arrived at the park and immediately I felt an eerie sensation. I had been there before with my other cousin Kim, but this time was undeniably different. It didn’t matter that the sun was shining above the bright blue sky, I sensed a darkness lingering. And it had nothing to do with the sticky Southern humidity. It was an overwhelming, odd, ineffable sensation. My eyes couldn’t help but focus on the trees behind the court. As if someone or something was watching us.
Nevertheless, after shooting for teams, we began a 2-on-2 immediately. When Mikey and I won, (I towered over them and Mikey was surprisingly pretty good) Tony wasn’t too happy about losing. In frustration, he bounced the basketball with both hands as hard as he could. The ball ended up on the other side of the fences surrounding the court and rolled into the bordering woods. None of the little squirts wanted to retrieve the ball, so as the big cuz I volunteered myself. Nothing to it right? Wrong!
As I walked towards the woods I couldn’t even locate the basketball. I stopped and scanned until I finally saw it, way deep among the trees. “How did it get all the way over there?” I mumbled beneath my breath. Then, while approaching the ball I heard a loud and distinct voice—“Hey!”—I turned around suddenly, but nothing was there. At first I wasn’t afraid, rather I was genuinely confused. It just made no damn sense, there was no one around. I swiveled my head in every direction and once again the deep, gravelly voice called out, “Hey!” This time I knew where it was coming from and crept towards the source until I spotted something in the bushes. I crouched and pushed some branches aside. And that’s when I noticed it. Buried under the shrubs was a tombstone! It stared back at me, weathered, cracked, moss-eaten. I picked my ass up, ran to the ball, scooped it and bolted back to the court.
Little Alex asked if we were going to play a rematch; I said, “Hell no”. After herding them back to the car, we left and never looked back. To this day I remember the voice. I recall the inexplicable feeling of the unknown energy, force, or spirit that was with us. I only recently shared this story with him and now, at 27, he asked why I didn’t tell him sooner. I thought hard about it and answered, “I guess I didn’t want you to get scared and piss yourself.”
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28rosetta.alhur.es
A service that grabs code samples from two chosen languages on RosettaCode and displays them side-by-side.
The code-fetching is done in real time and snippet-by-snippet (there is also a prefetch of which snippets are available in each language, so we only compare apples to apples).
This was my first Golang web application if I remember correctly.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ bcbb3e40:a494e501
2025-03-31 15:34:12
@ bcbb3e40:a494e501
2025-03-31 15:34:12|
 |
|:-:|
|MISSIAGGIA, Pietro; Jean Thiriart, el caballero euroasiático y la Joven Europa; Hipérbola Janus, 2025|
|
|:-:|
|MISSIAGGIA, Pietro; Jean Thiriart, el caballero euroasiático y la Joven Europa; Hipérbola Janus, 2025|Desde nuestros inicios los autores y temáticas relacionadas con la geopolítica nos han procurado atención e interés por parte del gran público y de los mass media, y no hay más que recordar el efecto que han venido teniendo nuestras obras de Aleksandr Duguin, en especial La geopolítica de Rusia y Proyecto Eurasia: teoría y praxis, sobre todo a raíz de nuestra presentación en Casa de Rusia en un ya lejano 2016, con la inestimable colaboración de Jordi de la Fuente como prologuista, trabajo que siempre reivindicamos desde nuestros medios por el prestigio, la calidad y brillantez de exposición del mismo.
Más allá de las obras del prestigioso y afamado filósofo y politólogo ruso, también hemos realizado otras incursiones en esta vertiente, que podríamos llamar «geopolítica alternativa», introduciendo las obras de otros notables autores como Claudio Mutti, Carlo Terracciano o Boris Nad. Con estos autores hemos tratado de profundizar en esa vía que se opone frontalmente, y radicalmente si se quiere, a los planteamientos derivados de la geopolítica atlantista y liberal que tiene su principal polo en Estados Unidos, haciendo especial hincapié en el subyugamiento que vienen ejerciendo desde 1945 en adelante respecto a una Europa convertida en un protectorado en una mera colonia.
Es por este motivo por el que la publicación de Jean Thiriart, el caballero euroasiático y la Joven Europa nos parece una obra totalmente pertinente en estos momentos, forma parte del desarrollo lógico de la línea editorial en la que estamos encauzados desde nuestros inicios, y viene a representar una de las múltiples vías en las que confluye la idea, profundamente schmittiana, de la política de los grandes espacios. En este caso la idea de una Europa unida, bajo un vasto proyecto que traspasa los estrechos límites del continente concebido como un apéndice más del «Occidente», de ese subproducto ideológico decadente y funcional a los intereses del otro lado del Atlántico. Para comprender la idea de una Europa unida, que comprenda a Rusia, y su enorme extensión territorial a lo largo de 17 millones de kilómetros cuadrados, y la importancia estratégica de su ubicación, es necesario recurrir al legado de Jean Thiriart, conocer su obra, pero también al hombre, pues una no se comprende sin el otro, en este caso hablamos de elementos correlativos.
|
 |
|:-:|
|Jean Thiriart (1922-1992)|
|
|:-:|
|Jean Thiriart (1922-1992)|¿Pero quién fue Jean Thiriart? Esta obra nos permite adentrarnos en aspectos biográficos, algunos de ellos poco conocidos para el gran público de habla hispana, y saber de su trayectoria, de la maduración de sus ideas, de su proyecto político y de las etapas que componen el desarrollo del mismo y que aparecen claramente diferenciadas: hablamos del proyecto político de unidad europea, que alcanza su concreción teórica en ¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres (1965, Editorial Mateu, Barcelona), en pleno apogeo de la organización Jeune Europe, que se convirtió en el órgano político a partir del cual creyó poder implementar su proyecto unitario a escala europeo, manteniendo una posición de independencia respecto a los dos pretendidos bloques antagónicos de Guerra Fría: Estados Unidos y la Unión Soviética. En esa época, estamos hablando del ecuador de los años 60, todo el mundo de la Contracultura, falsamente contestatario, estaba articulando su propio discurso, que tendría su expresión más nítida a través del ya conocido Mayo del 68 francés o la Primavera de Praga, durante el mismo año. Y si el movimiento de Nueva Derecha liderado por Alain de Benoist surgiría en lo sucesivo, ya en la década de los años 70, como una «reacción» frente a la «rebelión contracultural», no podemos obviar la importancia de un movimiento político como Jeune Europe, una organización política transnacional, a escala de la Europa occidental, con sus diferentes delegaciones en países como Francia, Italia, Alemania, la propia España además de, como es obvio, Bélgica, país de origen de nuestro autor.
Jean Thiriart ha sido etiquetado con reiteración como un político y teórico de «extrema derecha», se han hecho numerosos discursos interesados para vincularlo, por cuestiones de orden biográfico muy circunscritas a determinado periodo, con el fascismo y el nacionalsocialismo de entreguerras. Sin embargo, y como el lector podrá descubrir a lo largo de la presente obra, el pensamiento de nuestro autor está muy lejos de ser reducible a meras etiquetas, y en ningún caso mostró las filiaciones que se le atribuyen desde posicionamientos ideológicos, sino que, muy al contrario, vemos a un hombre de pensamiento racional y pragmático, poderosamente influenciado por la geopolítica y abierto a alianzas estratégicas más variadas, más allá de todo fundamentalismo ideológico. Es por este motivo que veremos a un Thiriart buscando sinergias y entendimiento entre círculos de izquierdas, antiimperialistas en una lucha concebida como «cuatricontinental». No en vano, muchos de los cuadros políticos que se formaron en Giovane Europa, la rama italiana, terminaron por militar incluso en organizaciones de extrema izquierda de inspiración maoísta. En el caso de España hubo un notable apoyo a la organización por parte de los falangistas más disidentes. De manera que Jean Thiriart representa una figura política compleja, con influencias variadas, que van desde los hermanos Strasser, pasando por Ernst Niekish o Vilfredo Pareto, e incluso, por Sieyès o Robespierre.
Es a partir de Jeune Europe cuando el nacionalismo europeo, la idea de una Europa unida desde Brest a Bucarest toma cuerpo. En la obra mencionada con anterioridad (¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres) Jean Thiriart ya nos presenta a través de unos trazos muy definidos el proyecto del comunitarismo nacional-europeo, la piedra angular de su proyecto político. La idea de un socialismo aristocrático y europeo, trascendiendo las fronteras del Estado-nación liberal decimonónico, y los particularismos nacionales, concebidos como formas obsoletas y «estrechas de miras», obstáculos a superar en la convergencia del Imperio europeo. Porque vemos a un Thiriart que potencia la estructura del Estado, del aparato de poder, tratando de potenciar, y restaurar naturalmente, el papel y la preponderancia de Europa como espacio de civilización en el mundo. Es un nacionalismo europeo que viene determinado por razones puramente geopolíticas, algo que también fue objeto de críticas, concretamente por parte del geopolítico austriaco Heinrich von Lohausen, y que también recogemos en el presente volúmen de la obra.
|
 |
|:-:|
|Ejemplar de una de las publicaciones más importantes de Joven Europa (Jeune Europe) cuya portada refleja el antiamericanismo y antiimperialismo característicos del nacionalismo europeo de la organización.|
|
|:-:|
|Ejemplar de una de las publicaciones más importantes de Joven Europa (Jeune Europe) cuya portada refleja el antiamericanismo y antiimperialismo característicos del nacionalismo europeo de la organización.|En este sentido, Thiriart no andaba nada desencaminado, en la medida que pensaba que solo los Estados de dimensiones continentales podrían ser capaces de defender su independencia y soberanía, y ejercer un poder en el mundo, frente a los antiguos nacionalismos europeos, totalmente anacrónicos y un factor de ruptura y desintegración del potencial europeo. En este contexto, se hace necesario eliminar el orden establecido en Yalta en 1945, que convierte a Europa en un vasallo de las grandes potencias vencedoras de la Segunda Guerra Mundial. De modo que luchar contra la ocupación estadounidense por un lado, y soviética por otro lado, fuese el principal leitmotiv del Partido Revolucionario Europeo, un partido histórico señala Thiriart, encargado de llevar a término la acción unificadora continental. Y es con este propósito con el que se tratan de concertar una serie de alianzas internacionales que llevó a Thiriart y su organización a tratar con personal diplomático y gubernamental de los países árabes no alineados, del régimen de Fidel Castro o incluso con emisarios del gobierno chino, como ocurrió en el famoso encuentro propiciado por Ceaucescu en Bucarest con Zhou En-Lai.
Quizás, uno de los puntos donde más desacuerdos encontramos con las teorías thiriartianas se encuentra en ciertos fundamentos que la articulan, en un modelo racionalista, materialista y pragmático, de hecho no debemos olvidar que Maquiavelo era uno de sus referentes, y con éste la posterior hornada de autores neomaquiavélicos como Vilfredo Pareto. El excesivo pragmatismo de sus planteamientos, un estatalismo exacerbado y sin concesiones a las particularidades de los pueblos, una suerte de centralismo jacobino, y la ausencia de un elemento trascendente capaz de dar una justificación metafísica a todo el proyecto nacional europeo constituyen, en nuestra opinión, una parte discutible y reformulable.
En otro terreno, como pueda ser el puramente económico, encontramos un proyecto anticapitalista en muchos de sus aspectos, frente al democratismo parlamentario liberal, y apoyándose en las teorías económicas de Johann G. Fichte o Friedrich List, rechazando cualquier organización económica transnacional que pueda mediatizar o convertir a Europa en objeto de sus actividades usurocráticas y depredatorias, colocando la soberanía e independencia económica europea en una de las máximas prioridades en este terreno.
Debemos destacar, porque es un elemento de debate especialmente interesante, el apartado del libro que se corresponde al escrito de Luc Michel, publicado en Italia bajo el título Da Jeune Europe alle Brigate Rosse, en el libro Parte II Historia de Jeune Europe (1962-1969), en el que se detallan las colaboraciones que comenzaron a sucederse entre la militancia de la delegación italiana, Giovane Europa, y círculos de extrema izquierda maoísta, y cómo muchos de los antiguos militantes nacional-europeos terminaron militando en organizaciones de esta facción ideológica, y nos referimos a casos tan representativos en la época como Claudio Orsoni o Pino Bolzano entre otros muchos.
La actividad proselitista de Jeune Europe en el último lustro de la década de los años 60, con la fundación del Partido Comunitario Europeo, nos legó una gran cantidad de publicaciones, entre las cuales destacaron La Nation Européenne, La Nazione Europea o Europa Combattente, cuyas portadas han servido para ilustrar las páginas interiores de nuestra obra, y que procuraron una actividad proselitista y de difusión de ideas que llegaron a imprimir semanal y mensualmente varios miles de ejemplares en Francia o en Italia.
Tras agotar todas las vías posibles de alianzas y convergencias, con encuentros poco afortunados, vemos a un Thiriart que prefiere adoptar otras vías para seguir construyendo el proyecto nacional-europeo más allá de la fórmula activista y del partido político. Este es el motivo por el cual, en los siguientes años, ya en la última etapa de su vida, veremos esa transición del político activista al teórico y al ideólogo como parte de una nueva estrategia dentro del proyecto político al que consagró buena parte de su vida, y es un hecho que comienza a apreciarse desde mediados de los años 70. Durante esta época la «Europa de Brest a Bucarest» se transforma y amplía en una «Europa desde Dublín a Vladivostok». Thiriart aborda ya abiertamente la integración del espacio soviético en una Europa unida que abarca un inmenso espacio territorial, capaz de unir el Océano Atlántico y el Océano Pacífico de un extremo a otro, el «Imperio Eurosoviético». No obstante, Thiriart siempre piensa en términos geopolíticos, y considera que este proceso de integración debe llevarse a cabo desde una revisión de la ideología soviética, desde una marcada desmarxistización de su socialismo, purgado de todo dogmatismo y elementos condicionantes derivados de la teoría del Estado formulada por el marxismo-leninismo para tomar en su lugar aquella de Thomas Hobbes.
A partir de este momento solamente hay un enemigo, el que representa el poder estadounidense y el dominio que éste ejerce sobre la Europa occidental. A partir de ese momento la URSS, bajo las premisas apuntadas por Thiriart, y desde una ideología soviética «desmarxistizada», es la que debe asumir el proyecto de integración europea. Todo este enfoque terminará conociendo su colofón final al final de la vida de Jean Thiriart, cuando éste se encuentre ya en sus último año de vida, en 1992, con una Unión Soviética ya periclitada y disuelta, con un país sumido en una crisis económica, política y social bajo el gobierno decadente de Yeltsin, con un poder notablemente menguado y a merced de las potencias extranjeras y las apetencias de las organizaciones financieras transnacionales. En este contexto tendrá lugar el conocido viaje de Jean Thiriart a Moscú, donde se encontrará, además de con la disidencia de Yeltsin, encabezada por el Partido Comunista dirigido por Gennadij Ziuganov y numerosas personalidades públicas del ámbito ruso, entre las que destacará por encima de todos el filósofo y politólogo Aleksandr Duguin, quien en la presente obra también reivindica la figura del belga como un contribuidor directo del pensamiento euroasiático. Además de medios de prensa, políticos e intelectuales rusos, nuestro autor también compartirá espacio con una pequeña delegación de la revista italiana «Orion», especializada en temática geopolítica, y representada por el padre de la geopolítica italiana, Carlo Terracciano. El encuentro no tendrá mayores consecuencias, y vendrá a significar el último acto de servicio de Jean Thiriart en su denodado esfuerzo por lograr la integración de Europa y Rusia en un poderoso bloque geopolítico capaz de hacer frente a la hegemonía estadounidense en el mundo.
Terminaremos este breve y sintético escrito de presentación con un fragmento de la obra que Jean Thiriart publicó en 1965 bajo el título ¡Arriba Europa!: Una Europa unida: un imperio de 400 millones de hombres, que nos parece de lo más adecuado para poner el punto final al presente texto:
Europa, este MILAGRO en la historia del hombre, este milagro que siguió al milagro griego, ha dado vida, con la prodigiosa fecundidad de su civilización irrepetible, a una cultura adoptada por el mundo entero. En la competencia surgida entre las grandes civilizaciones —occidental, india, china y japonesa— la nuestra ha aplastado a las demás.
La civilización es creadora de cultura. La cultura, en cambio, jamás ha creado civilización.
SOLO Europa posee la civilización; de ahí deriva su supremacía sobre los Estados Unidos y la Rusia comunista, que poseen únicamente la cultura nacida de nuestra civilización, como ha demostrado magistralmente Oswald Spengler.
Esta cultura, separada de su civilización, está condenada a la esterilidad, la cual se manifestará primero mediante una esclerosis y, posteriormente, mediante un retorno a la barbarie.
Políticamente dominada por Moscú o por Washington, la civilización europea se ve asfixiada y corre el riesgo de estancarse en su estado de simple cultura. Basta notar que todos los descubrimientos en el campo nuclear y astronáutico son obra de europeos. Todos buscan a los científicos europeos.
Solo una Europa políticamente unida puede proveer los medios de poder que garantizarán las condiciones históricas indispensables para la supervivencia de esta civilización.
Ninguna otra potencia, por otra parte, podría sustituir a Europa en su misión hacia la humanidad.
Artículo original: Hipérbola Janus, Presentación de «Jean Thiriart, el caballero euroasiático y la Joven Europa», de Pietro Missiaggia (TOR), 18/Mar/2025
-
 @ 52524fbb:ae4025dc
2025-03-31 15:26:46
@ 52524fbb:ae4025dc
2025-03-31 15:26:46 To most of us it's all about the sound of freedom, the innovation, it's technical implication, what if feels like in a decentralised environment. Now let's head into that which brings our fantasies to reality, Nostr which stands for "Notes and other stuffs Transmitted by Relays", is an open protocol designed for decentralised social networking
To most of us it's all about the sound of freedom, the innovation, it's technical implication, what if feels like in a decentralised environment. Now let's head into that which brings our fantasies to reality, Nostr which stands for "Notes and other stuffs Transmitted by Relays", is an open protocol designed for decentralised social networkingNost most Amazing Features:##
-
Decentralisation: compared to traditional social media platforms like like Twitter (X) and Instagram that rely on centralised servers, Nostr operates through a network of relays. These relays serves as servers that store and forward messages. This amazing feature of decentralisation aims to make the network completely resistant to censorship, most people would say how? To answer your question it's because no single individual control's it
-
User Control: ever thought of the purest feeling of freedom, well Nostr just gave you the space to experience. User's have total control over their data and identity.
-
Simplicity: why get stressed when Nostr got you covered? This protocol is designed to be relatively simple, making it easier for developers to build applications on top of it.

Nostr Relation to Bitcoin##
Who wouldn't want to be part of a community that embraces it's ethics in a dignified manner. Nostr has gained popularity within the Bitcoin community, and the Bitcoin Lightning Network is used for features like "Zaps" (which represents small payments or tips). There are also similarities in the philosophy of decentralization, that both bitcoin and Nostr share. Just like the saying goes, birds of the same feather flock together. This leads me to one of the best magnificent project, focused on building decentralisation media infrastructure, particularly within the Nostr ecosystem.

Yakihonne the future of the world##
YakiHonne is an amazing project focused on building decentralized media infrastructure, particularly within the Nostr ecosystem. It's mind blowing features includes:
-
Decentralized Media: YakiHonne aims to provide tools and platforms that support freedom and automation in content creation, curation, article writing and reporting. It leverages the decentralized nature of the Nostr protocol to achieve this amazing feat.
-
Nostr and Bitcoin Integration: YakiHonne is closely tied to the Nostr network, and it also incorporates Bitcoin functionality. This integration includes features related to the Lightning Network, enabling things like "zaps" (small Bitcoin payments) within the platform.
-
Mobile Application: YakiHonne offers a mobile application with an eye catching user interface simply designed to provide users with a smooth and intuitive Nostr experience. This app includes features like: -Support for various login options. -Content curation tools. -Lightning Network integration. -Long form article support.

Disadvantages of Traditional social media##
Lets go back to a world without the flute of freedom echoing in our hearts, where implementations are controlled by certain entities, reasons why traditional social media platforms hold not even a single stance compared to Nostr:
- Privacy Concerns:
Data Collection: Social media platforms collect vast amounts of user data, often without full transparency. This data can be used for targeted advertising, and sometimes, it can be compromised in data breaches. Which won't happen or be possible on yakihonne
-
Social Comparison and Low Self-Esteem: The over hyped and often unrealistic portrayals of life on social media can lead to feelings of inadequacy and low self-esteem. But on yakihonne you get to connect and grow with a community with specified goals bent on implementation
-
Misinformation and Fake News:
Spread of False Information: Social media platforms can be breeding grounds for misinformation and fake news, which can spread rapidly and have significant real-world consequences. Is that possible on yakihonne, well we all know the answer. 4. Centralized Control:
Censorship: Centralized platforms have the power to censor content, raising concerns about freedom of speech. Algorithm Bias: Algorithms can be biased, leading to unfair or discriminatory outcomes. This tells us why a decentralised media platform like yakihonne stands out to be the only media with a future.

Why Chose Nostr why chose yakihonne##
When considering Nostr and related projects like YakiHonne, the appeal stems largely from a desire for greater control, privacy, and freedom in online communication. Which from the points aligned above, gives us no second chance of thought, but the thought of being part of the Nostr community, active on a platform like yakihonne.
-
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Thoughts on Nostr key management
On Why I don't like NIP-26 as a solution for key management I talked about multiple techniques that could be used to tackle the problem of key management on Nostr.
Here are some ideas that work in tandem:
- NIP-41 (stateless key invalidation)
- NIP-46 (Nostr Connect)
- NIP-07 (signer browser extension)
- Connected hardware signing devices
- other things like musig or frostr keys used in conjunction with a semi-trusted server; or other kinds of trusted software, like a dedicated signer on a mobile device that can sign on behalf of other apps; or even a separate protocol that some people decide to use as the source of truth for their keys, and some clients might decide to use that automatically
- there are probably many other ideas
Some premises I have in my mind (that may be flawed) that base my thoughts on these matters (and cause me to not worry too much) are that
- For the vast majority of people, Nostr keys aren't a target as valuable as Bitcoin keys, so they will probably be ok even without any solution;
- Even when you lose everything, identity can be recovered -- slowly and painfully, but still --, unlike money;
- Nostr is not trying to replace all other forms of online communication (even though when I think about this I can't imagine one thing that wouldn't be nice to replace with Nostr) or of offline communication, so there will always be ways.
- For the vast majority of people, losing keys and starting fresh isn't a big deal. It is a big deal when you have followers and an online persona and your life depends on that, but how many people are like that? In the real world I see people deleting social media accounts all the time and creating new ones, people losing their phone numbers or other accounts associated with their phone numbers, and not caring very much -- they just find a way to notify friends and family and move on.
We can probably come up with some specs to ease the "manual" recovery process, like social attestation and explicit signaling -- i.e., Alice, Bob and Carol are friends; Alice loses her key; Bob sends a new Nostr event kind to the network saying what is Alice's new key; depending on how much Carol trusts Bob, she can automatically start following that and remove the old key -- or something like that.
One nice thing about some of these proposals, like NIP-41, or the social-recovery method, or the external-source-of-truth-method, is that they don't have to be implemented in any client, they can live in standalone single-purpose microapps that users open or visit only every now and then, and these can then automatically update their follow lists with the latest news from keys that have changed according to multiple methods.
-
 @ bcbb3e40:a494e501
2025-03-31 15:23:12
@ bcbb3e40:a494e501
2025-03-31 15:23:12|
 |
|:-:|
|BÉRARD, Bruno y LA FATA, Aldo; ¿Qué es el esoterismo?: Entre verdades y falsificacioines; Hipérbola Janus, 2025|
|
|:-:|
|BÉRARD, Bruno y LA FATA, Aldo; ¿Qué es el esoterismo?: Entre verdades y falsificacioines; Hipérbola Janus, 2025|Nos complace presentar al lector en lengua española una novedad de primer orden, y sobre un tema que viene siendo objeto de interés por parte de nuestra línea editorial, como es el esoterismo, que hemos abordado recientemente a través de un nuevo recopilatorio de la obra evoliana en Ensayos filosóficos, esotéricos y religiosos 1925-1931, donde hemos tratado de rescatar los textos de las primeras etapas en la formulación del pensamiento del Maestro Romano. No obstante, no es la primera aventura que hemos emprendido en este terreno, siempre complejo y acompañado de la etiqueta, popular y quizás vulgarizada, de lo «misterioso» y lo «oculto», aunque no somos nada sospechosos en ese sentido por banalizar o tratar de ofrecer un enfoque puramente literario del asunto, y ni mucho menos de simpatizar con aquellas vías que entroncan con el New age, donde las mixtificaciones y la voluntad de convertir el fenómeno esotérico en un producto de consumo más, como demanda el mercado, para satisfacer demandas materiales o simples modas de una masa sobresocializada son norma habitual.
Podríamos citar multitud de obras que están presentes en nuestro catálogo, como son El pensamiento esotérico de Leonardo, de Paul Vulliaud, El mundo mágico de los héroes, de Cesare della Riviera, una joya del esoterismo italiano del siglo XVII, en El maestro de la tradición perenne, de René Guénon, o en el ensayo de Gianluca Marletta OVNIS y alienígenas. Origen, historia y prodigio de una pseudorreligión, un ensayo de notable originalidad donde se abordan aspectos esotéricos, aunque sea de un modo más tangencial. También en la literatura, con la obra del gran mitólogo y literato Boris Nad, Una historia de Agartha y La muerte púrpura de Gustav Meyrink encontramos nuevas referencias al ámbito esotérico. De modo que podemos concluir en que el esoterismo forma parte esencial de nuestras publicaciones e intereses como editores, y contribuimos activamente a su difusión.
|
 |
|:-:|
|EVOLA, Julius; Ensayos filosóficos, esotéricos y religiosos: 1925-1931, Hiperbola Janus, 2024|
|
|:-:|
|EVOLA, Julius; Ensayos filosóficos, esotéricos y religiosos: 1925-1931, Hiperbola Janus, 2024|Una obra original
Por eso la presente obra, la que nos disponemos a presentar, cuyo título es ¿Qué es el esoterismo?: Entre verdades y falsificaciones, de Bruno Bérard y Aldo La Fata, viene a ser una obra muy necesaria y clarificadora en la comprensión del esoterismo en todas sus dimensiones, en la complejidad de sus particulares, y en sus múltiples manifestaciones. Quizás en el mundo de habla hispana el esoterismo es un fenómeno que no ha obtenido su merecida atención, y nuestros autores en este ámbito, como es el caso de un Ramón Llull entre otros, no sean objeto de la atención que merece, y las actividades esotéricas, a nivel de asociaciones, comunidades u otras formas de organización, tampoco sean especialmente conocidas, ni cuenten con una actividad reconocida. Es posible, como señala La Fata, que haya ciertas reticencias dentro del mundo católico, acostumbrado a la ortodoxia y la guía espiritual de la Iglesia, y que cualquier tipo de «desviación» hacia formas más individuales y «libres» de vivir ciertas formas iniciáticas, mucho más sutiles, provoquen el rechazo y la incomprensión general. No obstante, como también se encargan de aclarar nuestros autores, el esoterismo comprende una dimensión diferenciada, implica un esfuerzo que no todos están dispuestos a acometer, y finalmente, no es tampoco un camino de felicidad y de frutos seguros, implica una transformación interior y la asunción de unas prácticas y procedimientos que no son aptos para cualquiera. Digamos que el esoterismo es un camino, una vía, que a diferencia de las «religiones populares», exotéricas, supone un arduo camino que viene marcado por un principio vertical y aristocrático de la existencia, o al menos así queremos verlo nosotros. El incremento de la capacidad de discernimiento, aunar lo visible con lo invisible, y ser capaz de superar límites vedados al común, no por simple vanidad ni por «crecimiento personal», tal y como se concibe en las aburguesadas y decadentes sociedades actuales, sino como parte de un proceso de aprendizaje, de autoconocimiento y de liberación. No nos cabe duda alguna de la necesidad de restaurar los antiguos vínculos con lo Alto, las vías que quedaron cerradas y que nos han limitado progresivamente al exclusivo y estrecho ámbito de la materialidad.
|
 |
|:-:|
|RIVIERA, Cesare della; El mundo mágico de los héroes; Hipérbola Janus, 2022|
|
|:-:|
|RIVIERA, Cesare della; El mundo mágico de los héroes; Hipérbola Janus, 2022|La obra emplea el recurso de la entrevista/diálogo, que aporta frescura y fluidez al texto «simplificando», o más bien haciendo más accesibles y comprensibles elementos relacionados con el esoterismo, que de otro modo resultarían excesivamente complejos para una parte del público lector poco familiarizado con la materia. Este dinamismo se ve complementado por la riqueza de matices e ideas que se van introduciendo de manera progresiva, evitando que el lector pueda verse abrumado por la avalancha de ideas y contenidos. Las preguntas de Bruno Bérard, siempre inteligentes, incisivas y pertinentes, además de ordenadas y bien estructuradas, favorecen la continuidad y el dinamismo en la exposición de los temas, ejerciendo de guía en la conversación. De ahí que el libro sea apto para diferentes niveles, tanto para aquellos que desconocen el esoterismo, como para quienes se encuentran familiarizados con el tema. Aldo La Fata, de acuerdo con su dilatada y extensa trayectoria en la materia, nos hace reflexiones teóricas de enorme valor, que entrelaza con su propia experiencia y trayectoria en el estudio del esoterismo. Sin lugar a dudas este aspecto nos permite ver una vertiente más humana e íntima, en la que se incluyen anécdotas personales y biográficas que siempre permiten una mayor conexión con el lector a través de la mezcla de hechos vitales y erudición teórica.
La entrevista que nos ofrecen Bruno Bérard y Aldo La Fata nos permite explorar la relación dialéctica que se genera entre el esoterismo y otros ámbitos como la religión, la ciencia o la filosofía. Todas las cuestiones se abordan desde enfoques muy concretos, abordando problemáticas particulares, que dan lugar a reflexiones más amplias evitando las simplificaciones e invitando a reflexiones mucho más profundas. De ahí la función de introducción y guía a la que nos venimos refiriendo.
Estos aspectos que acabamos de enumerar con anterioridad revelan un notable esfuerzo pedagógico por parte de los autores para acercarnos al estudio del esoterismo, nos aporta las herramientas necesarias, parafraseando el título de la obra, para discernir entre un verdadero esoterismo y sus falsificaciones.
Más allá de estos aspectos formales, que consideramos que es importante destacar, porque en ellos reside el éxito de la obra, en un planteamiento que resulta original, a la par que ameno y de gran interés, debemos considerar otros aspectos que hacen más referencia al contenido. «¿Qué es el esoterismo? Entre verdades y falsificaciones» pretende, como decíamos, clarificar qué es el esoterismo, cuales son sus particulares, sus características y atributos, su naturaleza más íntima, como fenómeno espiritual y filosófico en sus aspectos más profundos, que podemos remontar a épocas muy remotas y lejanas en el tiempo. Pero el esoterismo aparece en ocasiones fuertemente imbricado en otras estructuras de pensamiento, de tipo tradicional, como son las grandes religiones (Cristianismo, Islam, Judaísmo etc) y otros conceptos como la mística y la metafísica, cuyas relaciones hay que desentrañar.
La importancia de René Guénon
Aldo La Fata nos libera desde el principio de posibles equívocos al enfatizar que el verdadero esoterismo no es una simple acumulación de conocimientos secretos o rituales exóticos, sino una vía de trascendencia espiritual basada en el rigor y la autenticidad. A este respecto René Guénon aparece como uno de los grandes esoteristas de nuestro tiempo, en la medida que fue el gran intérprete y codificador de estos conocimientos, una figura que marcó un antes y un después en la comprensión de este ámbito, especialmente por su rigor conceptual y su capacidad para distinguir entre lo auténtico y lo falso en las tradiciones espirituales. A tal respecto podemos poner como ejemplo sus contundentes análisis de las corrientes ocultistas, especialmente del espiritismo o del teosofismo, en diferentes obras. Podemos decir a este respecto que Guénon hizo una distinción entre esoterismo y ocultismo, disociando el significado del primero de prácticas superficiales y desviadas, mientras que definió el esoterismo como una vía de conocimiento sagrado y trascendente. En este sentido fue una labor fundamental para evitar confusiones con mixtificaciones modernas y pseudoesoterismos como aquellos relacionados con el New Age.
|
 |
|:-:|
|GUÉNON, René; El Maestro de la Tradición Perenne: Antología de artículos guenonianos; Hipérbola Janus, 2021|
|
|:-:|
|GUÉNON, René; El Maestro de la Tradición Perenne: Antología de artículos guenonianos; Hipérbola Janus, 2021|Paralelamente, y con ello queremos dignificar la figura de René Guénon, el tradicionalista francés también nos abrió las fuentes de un vasto conocimiento espiritual, expresión de una «Tradición primordial», a cuyos orígenes prístinos siempre deberíamos aspirar, y cuya impronta impregna por completo religiones, culturas y formas de civilización no modernas, claro está. Y otro elemento fundamental, y que en la presente obra se considera de vital importancia, es que René Guénon considera el esoterismo no como una vía interna propia de la religión, sino como una vía complementaria que permite acceder a la esencia divina más allá de las formas externas. Para Aldo La Fata no se trata de una mera referencia intelectual, sino una figura que marcó su propio rumbo dentro del estudio del esoterismo. A través de obras como Los símbolos de la ciencia sagrada, La Fata descubrió la profundidad y la coherencia del pensamiento guenoniano, así como la idea de que el esoterismo actúa como el «pegamento» que conecta todas las tradiciones espirituales. Esta visión le permitió entender el esoterismo como algo inseparable de la religión, aunque con una profundidad y una exigencia mayores.
¿Qué es el esoterismo?
El término esoterismo tiene sus raíces etimológicas en el griego esôterikos, que implica un «ir hacia dentro» y que se contrapone a una variante exterior que definimos como «exoterismo», que se encuentra más vinculado al ámbito de la religión. Se trata de un conocimiento que no atiende a un principio puramente intelectual y discursivo sino que apunta a una vivencia directa y sapiencial de lo trascendente. Lejos de la acumulación de saberes ocultos y rituales, lo que prima en la experiencia de lo esotérico es la conexión directa con lo trascendente y lo divino a través de la práctica espiritual.
De hecho hay tres aspectos que nuestros autores destacan a lo largo de la obra respecto al esoterismo, y que nos parecen fundamentales:
- Interioridad: Supone un movimiento continuo hacia el interior, de exploración e introspección, en el que se tratan de derribar límites y obstáculos. Atendiendo a un dinamismo que huye de lo fijo y de lo estático.
- Profundización: La búsqueda de significados más profundos tras la realidad cotidiana, buscando ir más allá de la pura exterioridad de las cosas
- Relación con el exoterismo: Podemos considerarlo opuesto en sentido relativo al esoterismo, como una dimensión más externa y visible de las religiones, aunque este último (el esoterismo), no puede sobrevivir sin el apoyo de una tradición religiosa.
En relación al último punto debemos destacar, como advierten Bérard y La Fata, que pese a todo no podemos entender el esoterismo como una parte de las religiones, sino que tiene su propia función y objetivos, que no es otro que el que ya hemos mencionado con anterioridad: establecer una conexión directa con la verdad que irradia del principio universal y divino.
|
 |
|:-:|
|VULLIAUD, Paul; El pensamiento esotérico de Leonardo da Vinci; Hipérbola Janus, 2024|
|
|:-:|
|VULLIAUD, Paul; El pensamiento esotérico de Leonardo da Vinci; Hipérbola Janus, 2024|Otro aspecto interesante de la obra es el que nos habla de las relaciones entre esoterismo y metafísica, en el que el primero pretende ser también una vía de acceso al dominio del segundo. El esoterismo, como ya hemos visto, tiene como principal propósito trascender las categorías del mundo material para proyectarse en lo universal, y en este sentido comparte también objetivos con la metafísica, que pretende superar las limitaciones de la experiencia humana ordinaria y de acceder a las verdades primordiales que estructuran la realidad. Ambos apuntan a la raíz de todo lo existente, al absoluto. Las divergencias las hallamos en la forma o en el método para alcanzar estas verdades trascendentes, que en el caso del esoterismo nos remiten a símbolos, rituales y experiencias vivenciales que permiten al practicante interiorizar verdades universales.
De este modo, esoterismo y metafísica se nos presentan como realidades no opuestas, sino complementarias. La metafísica nos ofrece un marco conceptual y doctrinal para entender lo absoluto, mientras que el esoterismo se centra en su realización interna. En términos guenonianos, el esoterismo representa los aspectos operativos de la metafísica.
De modo que podemos decir que la metafísica aborda el tema trascendente desde una perspectiva conceptual, sin esa parte vivida de la experiencia en el conocimiento de lo universal. El esoterismo, por su parte, aporta esa contraparte que nos remite a la experiencia humana que permite al individuo acceder o ponerse en conexión con lo divino a través de su propio ser, de manera directa y vívida. Es un camino que el sujeto individual emprende para lograr una transformación interior.
Paralelamente, no podemos obviar dentro de todos estos procesos la participación de un elemento fundamental, como es la intuición suprarracional, que podríamos considerar como la herramienta que conecta al esoterista directamente con la fuente del conocimiento trascendente y universal, en lugar de hacerlo directamente a través de teorías o conceptos que siempre resultan más abstractos y difíciles de comprender en su vertiente más «discursiva». Al mismo tiempo, las relaciones que se establecen entre esoterismo y metafísica nos permiten poner en contacto las tradiciones religiosas con el conocimiento universal. Según La Fata, inspirándose en el legado de la obra de Frithjoff Schuon, cada tradición espiritual tiene una dimensión metafísica que puede ser comprendida y realizada a través del esoterismo, como un medio para acceder a la esencia inmutable de todas las formas religiosas.
Otro aspecto que esoterismo y metafísica comparten es la meta de superar la dualidad entre sujeto y objeto: Mientras que la metafísica conceptualiza esta unión como una verdad última, el esoterismo busca experimentarla directamente a través de la contemplación, el símbolo y la práctica espiritual.
Los autores
|
 |
|:-:|
|Aldo La Fata|
|
|:-:|
|Aldo La Fata|Aldo La Fata (1964) es un estudioso del esoterismo, el simbolismo y la mística religiosa, con una trayectoria de varias décadas dedicada al análisis y divulgación de estas disciplinas. Ha sido jefe de redacción de la revista Metapolitica, fundada por Silvano Panunzio, y actualmente dirige Il Corriere Metapolitico. Su trabajo destaca por una aproximación rigurosa y una mirada crítica a las corrientes contemporáneas del esoterismo, rescatando su sentido más profundo y tradicional. Entre sus obras más relevantes se encuentran Silvano Panunzio: vita e pensiero (2021) y Nella luce dei libri (2022), donde explora la intersección entre espiritualidad, simbolismo y pensamiento tradicional.
|
 |
|:-:|
|Bruno Bérard|
|
|:-:|
|Bruno Bérard|Bruno Bérard (1958), es doctor en Religiones y Sistemas de Pensamiento por la École Pratique des Hautes Études (EPHE), es un destacado especialista en metafísica. Autor de múltiples ensayos, ha desarrollado una profunda reflexión sobre la naturaleza del conocimiento espiritual y su relación con las tradiciones religiosas. Algunas de sus obras más importantes, traducidas a diversas lenguas, incluyen A Metaphysics of the Christian Mystery (2018) y Métaphysique du paradoxe (2019). Actualmente, dirige la colección Métaphysique au quotidien en la editorial L’Harmattan de París, consolidándose como una referencia en el estudio de la metafísica contemporánea.
En ¿Qué es el esoterismo?: Entre verdades y falsificaciones, asistimos a una presentación del tema tratado desde un conocimiento profundo y dilatado del tema, en la que ambos autores combinan la experiencia y el conocimiento que atesoran sobre el esoterismo y otros temas anejos, ofreciéndonos sus interpretaciones y enfoques particulares, y al mismo tiempo mostrando una gran capacidad de síntesis en la exposición de los temas tratados, que se inscriben en una multitud de tradiciones religiosas y espirituales de enorme complejidad. En este último punto reside también gran parte del valor de la obra, que constituye una novedad editorial especialmente relevante en su ámbito en lengua hispana.
Artículo original: Hipérbola Janus, Presentación de «¿Qué es el esoterismo?: Entre verdades y falsificaciones» (TOR), 6/Feb/2025
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28lnurl-auth explained
You may have seen the lnurl-auth spec or heard about it, but might not know how it works or what is its relationship with other lnurl protocols. This document attempts to solve that.
Relationship between lnurl-auth and other lnurl protocols
First, what is the relationship of lnurl-auth with other lnurl protocols? The answer is none, except the fact that they all share the lnurl format for specifying
httpsURLs.In fact, lnurl-auth is very unique in the sense that it doesn't even need a Lightning wallet to work, it is a standalone authentication protocol that can work anywhere.
How does it work
Now, how does it work? The basic idea is that each wallet has a seed, which is a random value (you may think of the BIP39 seed words, for example). Usually from that seed different keys are derived, each of these yielding a Bitcoin address, and also from that same seed may come the keys used to generate and manage Lightning channels.
What lnurl-auth does is to generate a new key from that seed, and from that a new key for each service (identified by its domain) you try to authenticate with.

That way, you effectively have a new identity for each website. Two different services cannot associate your identities.
The flow goes like this: When you visit a website, the website presents you with a QR code containing a callback URL and a challenge. The challenge should be a random value.

When your wallet scans or opens that QR code it uses the domain in the callback URL plus the main lnurl-auth key to derive a key specific for that website, uses that key to sign the challenge and then sends both the public key specific for that for that website plus the signed challenge to the specified URL.

When the service receives the public key it checks it against the challenge signature and start a session for that user. The user is then identified only by its public key. If the service wants it can, of course, request more details from the user, associate it with an internal id or username, it is free to do anything. lnurl-auth's goals end here: no passwords, maximum possible privacy.
FAQ
-
What is the advantage of tying this to Bitcoin and Lightning?
One big advantage is that your wallet is already keeping track of one seed, it is already a precious thing. If you had to keep track of a separate auth seed it would be arguably worse, more difficult to bootstrap the protocol, and arguably one of the reasons similar protocols, past and present, weren't successful.
-
Just signing in to websites? What else is this good for?
No, it can be used for authenticating to installable apps and physical places, as long as there is a service running an HTTP server somewhere to read the signature sent from the wallet. But yes, signing in to websites is the main problem to solve here.
-
Phishing attack! Can a malicious website proxy the QR from a third website and show it to the user to it will steal the signature and be able to login on the third website?
No, because the wallet will only talk to the the callback URL, and it will either be controlled by the third website, so the malicious won't see anything; or it will have a different domain, so the wallet will derive a different key and frustrate the malicious website's plan.
-
I heard SQRL had that same idea and it went nowhere.
Indeed. SQRL in its first version was basically the same thing as lnurl-auth, with one big difference: it was vulnerable to phishing attacks (see above). That was basically the only criticism it got everywhere, so the protocol creators decided to solve that by introducing complexity to the protocol. While they were at it they decided to add more complexity for managing accounts and so many more crap that in the the spec which initially was a single page ended up becoming 136 pages of highly technical gibberish. Then all the initial network effect it had, libraries and apps were trashed and nowadays no one can do anything with it (but, see, there are still people who love the protocol writing in a 90's forum with no clue of anything besides their own Java).
-
We don't need this, we need WebAuthn!
WebAuthn is essentially the same thing as lnurl-auth, but instead of being simple it is complex, instead of being open and decentralized it is centralized in big corporations, and instead of relying on a key generated by your own device it requires an expensive hardware HSM you must buy and trust the manufacturer. If you like WebAuthn and you like Bitcoin you should like lnurl-auth much more.
-
What about BitID?
This is another one that is very similar to lnurl-auth, but without the anti-phishing prevention and extra privacy given by making one different key for each service.
-
What about LSAT?
It doesn't compete with lnurl-auth. LSAT, as far as I understand it, is for when you're buying individual resources from a server, not authenticating as a user. Of course, LSAT can be repurposed as a general authentication tool, but then it will lack features that lnurl-auth has, like the property of having keys generated independently by the user from a common seed and a standard way of passing authentication info from one medium to another (like signing in to a website at the desktop from the mobile phone, for example).
-
-
 @ bcbb3e40:a494e501
2025-03-31 15:02:58
@ bcbb3e40:a494e501
2025-03-31 15:02:58Traducción por Francisco de la Torre.
|
 |
|:-:|
|Los representantes de la derecha sionista europea que forman parte de «Patriots» reunidos en Bruselas el pasado mes de diciembre de 2024.|
|
|:-:|
|Los representantes de la derecha sionista europea que forman parte de «Patriots» reunidos en Bruselas el pasado mes de diciembre de 2024.|Entre los efectos que probablemente producirá en Europa la nueva administración estadounidense, es previsible el fortalecimiento del ala derecha del colaboracionismo atlantista que, después de haberse posicionado decididamente a favor de Donald Trump durante su presidencia 2017-2021, en el transcurso de la administración Biden abogó fervientemente por su regreso a la Casa Blanca y acogió su victoria electoral con gran júbilo. A finales de octubre de 2024, en el grandioso mitin preelectoral a favor de Trump celebrado en el Madison Square Garden de Nueva York, asistió una representante del grupo parlamentario europeo Patriots for Europe, que viajó a Estados Unidos para esa ocasión especial. En un vídeo publicado en la página X (antes twitter) de los Patriots, varios eurodiputados del mencionado grupo expresaron su identidad con los puntos de vista de Trump y auspiciando su reelección: el austriaco Harald Vilimsky (Freiheitliche Partei Österreichs), el checo Ondrej Knotek (Año 2011) el español Jorge Buxade (Vox), el holandés Tom Vandendriesche (Vlaams Belang), la polaca Anna Bryłka (Ruch Narodowy) y, por Hungría, Tamás Deutsch (Fidesz).
Este último es, sin duda, la personalidad más eminente del grupo de los Patriots que viajaron a Nueva York: originario de una familia judía de Budapest, en 1988 Tamás Deutsch junto con Viktor Orbán están entre los fundadores de Fidesz —Fiatal Demokraták Szövetsége (Alianza de los jóvenes demócratas), en la que ocupó el cargo de vicepresidente. El Fidesz ha tejido durante mucho tiempo una red de lazos con el Partido Republicano de los Estados Unidos y con el think tank conservador Heritage Foundation, mientras que el gobierno de Viktor Orbán organizó las tres últimas ediciones anuales de la CPAC en Hungría (Conservative Political Action Conference), un encuentro de políticos de derechas de varios países[^1].
Patriots for Europe o Patriots.eu, denominación que recuerda al de los misiles aire-tierra estadounidenses (el MIM-104 Patriots), es, por tanto, el nombre oficial del grupo político de la derecha liberal-conservadora, populista y euroescéptica, nacido en julio de 2024 (primero como alianza y luego como grupo parlamentario europeo) por iniciativa del primer ministro húngaro Viktor Orbán, el exprimer ministro checo Andrej Babiŝ y del exministro del interior austriaco Herbert Kickl. Como representantes de sus respectivos partidos (Fidesz, Año 2011, Freiheitliche Partei Österreichs), Orbán, Babiŝ y Kickl firmaron un texto ideológico titulado: A Patriotic Manifesto for a European Future[^2], según la cual la única política europea legítima es aquella que, enraizada en la pluralidad de las diferentes naciones, proteja su herencia grecorromana-judeocristiana preservando su identidad, tradiciones y costumbres.
Al núcleo inicial de los Patriots se unió el partido portugués ¡Arriva! (¡Chega!), el Partido húngaro Popular Demócrata Cristiano (Kereszténydemokrata Néppárt), el partido español Vox, el Partido por la Libertad (Partij voor de Vrijheid) holandés, el Partido Popular Danés (Dansk Folkeparti), el interés Flamenco (Vlaams Belang), la Reunión Nacional (Rassemblement National) francés y, por Italia, la Liga para Primer Ministro Salvini.
Constituido formalmente, el grupo parlamentario recibió una posterior adhesión del diputado griego de Voz de la Razón (Foní Logikis), del diputado de Primero Letonia (Letvija pirmajâ prohibir), de los dos diputados del Movimiento Nacional polaco (Ruch Narodowy) y de los dos diputados checos del Juramento (Přísaha) y de los Automovilistas por sí mismos (Motoristé sollozoê). Presidente del grupo parlamentario Patriots.eu, que cuenta con un total de ochenta y seis diputados[^3], es Jordan Bardella, presidente de la Rassemblement National; pero la personalidad más notable y prestigiosa de los Patriots es, sin duda, el primer ministro húngaro Viktor Orbán.
En cuanto a la línea de política exterior seguida por Viktor Orbán, cabe recordar que fue durante su primer mandato, en 1989, cuando Hungría se unió a la OTAN junto con la República Checa y Polonia. La pertenencia a la organización militar de la Alianza Atlántica implicó la participación húngara en la guerra de Kosovo en Yugoslavia, así como la contribución de Hungría en las misiones de la ISAF y en la guerra en Irak en apoyo de la intervención estadounidense. Por otro lado, no deja de ser significativo que en junio de 2011, durante la visita de Condoleezza Rice a Budapest, se inaugurara una estatua del presidente estadounidense Ronald Reagan en la céntrica Plaza de la Libertad (Szabadság tér). «Hoy —dijo Orbán en esa ocasión— erigimos aquí una estatua al hombre, al líder, que cambió y renovó este mundo creando un nuevo mundo para nosotros en Europa Central, un hombre que creía en la libertad, en la fuerza moral de los hombres libres, y creía que los muros que obstruyen el camino a la libertad pueden ser derribados».
En los años de la primera administración Trump, Orbán estableció una relación privilegiada con la Casa Blanca: en 2019 fue recibido calurosamente por el presidente estadounidense, quien declaró su apoyo al «soberanismo» europeo, del que Orbán era ya el exponente más puntero. El primer ministro húngaro, que más tarde expresó varias veces la esperanza de volver a ver a Trump como líder de los Estados Unidos, se reunió con él de nuevo en Mar-a-Lago de Palm Beach en marzo de 2024 y al final de la visita escribió en una publicación: «¡Hacer que América vuelva a ser grande, señor presidente!»[^4].
El entendimiento entre Trump y Orbán fue favorecido por Benjamin Netanyahu, quien ha tenido una estrecha relación con el actual primer ministro húngaro desde 2005, cuando Orbán estaba en la oposición y Netanyahu era ministro de Finanzas. Esta relación, que Orbán ha utilizado para neutralizar las iniciativas hostiles de las ONG’s de Soros (quien financió a Fidesz desde 1992 a 1999), ha acentuado progresivamente la posición proisraelí de Budapest, hasta el punto que Hungría junto a Austria, Croacia y República Checa, se han alineado con Estados Unidos e Israel votando en contra de la resolución propuesta por la ONU para el alto el fuego en la Franja de Gaza. Cuando László Toroczkai, jefe del partido Mi Hazánk (Nuestra Patria), preguntó a Orbán en el Parlamento por qué Hungría había votado en contra, el primer ministro le respondió: «La política exterior es complicada, enfréntate solo si entiendes de lo que estamos hablando»[^5].
El presidente de Patriots, Jordan Bardella, no es menos pro-sionista. «Reconocer un Estado palestino significaría reconocer el terrorismo», dijo Bardella, quien antes de las elecciones francesas había asegurado que, si llegaba a ser primer ministro, sería «un escudo para los compatriotas judíos contra un islamismo que no solo quiere separar la República, sino conquistarla»[^6]. Por su parte, Marine Le Pen, madrina política de Bardella, declaró: «Es absolutamente legítimo que Israel quiera erradicar al grupo terrorista armado Hamas y que se dote de medios para hacerlo»[^7].
En cuanto a la Liga de Salvini como primer ministro, sus posiciones pro-trumpistas y pro-sionistas siempre se han caracterizado por un extremismo descarado. «Nunca he ocultado —dijo Salvini antes de las elecciones estadounidenses— mi esperanza en una victoria republicana, por mil razones (...) hablamos [con Trump] a más tardar hace unas semanas. Nunca he ocultado mi simpatía humana y mi sintonía cultural»[^8]. Y sobre el genocidio en curso en Palestina, Salvini dijo: «Nuestros pensamientos están con el pueblo israelí (...) Recordar siempre el derecho de Israel a existir, a defenderse y a convivir finalmente en paz con sus pueblos vecinos, contra el horror del terrorismo islámico»[^9]. El 6 de octubre de 2024, al final de su discurso desde el escenario de Pontida, Salvini posó para una foto con los Patriots presentes en la manifestación de la Liga Norte: además de Viktor Orbán, estuvieron el holandés Geert Wilders, el portugués André Ventura, la austriaca Marlene Svazek, el español Antonio Fúster y el general Roberto Vannacci. Enviaron mensajes en vídeo de apoyo y solidaridad tanto Jordán Bardella en nombre de Rassemblement national como el ex-presidente brasileño Jair Bolsonaro.
También Geert Wilders (Partij voor de Vrijheid), que en 2009 recibió el Premio Oriana Fallaci por producir un cortometraje de propaganda antiislámica, es conocido también por su extremismo prosionista. «Jerusalén, Judea y Samaria —en su opinión— son todas de Israel (...) La patria de los palestinos es el Reino de Jordania (...) Obama y Kerry deben dejar de criticar a Israel por los asentamientos. Judea y Samaria pertenecen a los israelíes»[^10]. En el programa de Wilders, «distinguiéndose durante dos décadas por su lucha contra la islamización —escribe complacido un sitio web sionista— está también el reconocimiento de Jerusalén como capital de Israel, con el traslado de la embajada holandesa»[^11].
André Ventura, presidente de ¡Chega!, reiteró en Polonia la posición prosionista de su partido, declarando convencido: «Estamos con Israel y permaneceremos junto a Israel en esta batalla por los derechos humanos y la democracia»[^12]. A quienes lo comparan con Donald Trump y Jair Bolsonaro, André Ventura responde: «Estoy acostumbrado a estas comparaciones. Estas son las ideas en las que creo»[^13]. En cuanto a la guerra en Ucrania, el líder de la lista ¡Chega! en las elecciones europeas, Antonio Tânger Corrêa, dijo que «la derrota de Ucrania sería la derrota de todo Occidente y de Portugal, en caso de extrema necesidad»[^14], enviarían a sus tropas.
Marlene Svazek representó a la Freiheitliche Partei Österreichs en Pontida, cuyos «excelentes contactos»[^15] con la derecha israelí están garantizados por David Lasar, miembro del Consejo Nacional (Nationalrat) del partido austriaco. Lasar no es el único judío en el FPÖ: también es judío el ex-secretario general del partido y ex-parlamentario europeo Peter Sichrovsky, quien ha negado ser un agente del Mossad, pero ha admitido haber tenido «muchas reuniones con funcionarios israelís»[^16].
José Antonio Fúster es el nuevo presidente de Vox Madrid. El jefe del partido que lo representa, Santiago Abascal, encabezó una delegación a Israel en 2023 que se reunió con dos ministros de Tel Aviv. «Durante la visita, Abascal ha transmitido el apoyo y la solidaridad de España al Primer Ministro israelí Benjamin Netanyahu, y ha defendido la urgente necesidad de acabar con Hamas que, según Abascal, es un grupo terrorista que «encarna el mal absoluto»[^17]. Tras la reunión de la delegación de Vox con Netanyahu, el candidato electoral Jorge Buxadé Villalba afirmó que las acciones genocidas cometidas por el régimen sionista en la Franja de Gaza son «operaciones antiterroristas» que deben continuar «hasta que no quede ni un solo terrorista»[^18].
En cuanto a Roberto Vannacci, elegido diputado del Parlamento Europeo en las listas de la Liga por Salvini, su currículum vitae patriot puede jactarse de una participación activa en las operaciones de EE.UU. en Oriente Medio. El general comandó durante dos turnos (2005-2006) el Special Forces Task Group en Irak y fue el primer comandante de la Task Force 45 en Afganistán en 2013, poco antes de la transición de la International Security Assistance Force a la Resolute Support Mission, Vannacci asumió el cargo de jefe del Estado Mayor de las fuerzas especiales de la OTAN, «una organización que ha garantizado la paz durante más de cincuenta años, una alianza política y militar que ha funcionado bien»[^19]. Habiendo prestado sus servicios a los Estados Unidos «para la estabilización de Irak»[^20] como Deputy Commanding General y Director of Training, el 21 de agosto de 2018, Vannacci fue galardonado con la Legion of Merit, la condecoración militar estadounidense creada por el presidente Franklin D. Roosevelt. Su consigna antes y después de la elección de Trump ha sido: «Go, Donald, go!».
[^1]: Cfr. C. Mutti, Alla destra degli USA, «Eurasia» 1/2023.
[^2]: Después de la confluencia de los grupos de Identity and Democracy en el grupo de Patriots, se aprobó una nueva versión del manifiesto político. Véase https://patriots.eu/manifesto
[^3]: Freiheitliche Partei Österreichs (Austria), 6; Vlaams Belang (Bélgica), 3; Dansk Folkeparti (Dinamarca), 1; Rassemblement National (Francia), 30; Foni Logikis (Grecia), 1; Fidesz - Magyar Polgári Szövetség (Hungría), 10; Kereszténydemokrata Néppárt (Hungría), 1; Liga para Salvini Premier (Italia), 8; Letvija primajâ vietâ (Letonia), 1; Partij voor de Vrijheid (Países Bajos), 6; Ruch Narodowy (Polonia), 2; ¡Chega! (Portugal), 2; ANO (República Checa), 7; Automovilistaé sobê (República Checa), 1; Přísaha (República Checa), 1; Vox (España), 6.
[^4]: Angela Napoletano, La «visita». Orbán incorona Trump: «Lui è il presidente della pace», avvenire.it, 9 marzo 2024.
[^5]: András Dezsô, The roots of Orbán’s strong bond with Israel and its PM, https://balkaninsight.com, 14 de noviembre de 2023.
[^6]: Bardella, «riconoscere Palestina è riconoscere terrorismo». «Sarò uno scudo per i nostri connazionali ebrei», ANSA, 26/6/2024.
[^7]: Mauro Zanon, Sorpresa, lo «scudo» degli ebrei in Francia è il partito della Le Pen, tempi.it, 27 de octubre de 2023.
[^8]: Stefano Baldolini, Salvina punta su Trump: «Spero che vinca. Andrò negli Usa prima del voto». Tensioni con Meloni? «Governo durerà 5 anni», repubblica.it, 13 de julio de 2024.
[^9]: Nova.News, 7 de octubre de 2024.
[^10]: Elezioni in Olanda, che è il sovranista Wilders: anti-Islam, contro l’Ue e sostenitore del Grande Israele, www.open.online, 23 de noviembre de 2023.
[^11]: www.informazionecorretta.com, 26 de octubre de 2024.
[^12]: www.agenzianova.com, 6 de octubre de 2024.
[^13]: Especial: André Ventura. «Sou contra o aborto mas nunca condenaria uma mulher que aborta», «Jornal SOL», 12 de julio de 2022.
[^14]: Ventura admite tropas portuguesas na Ucrânia e tem uma posição clara sobre Putin, «CNN Portugal», 11 de marzo de 2024.
[^15]: Sophie Makris, Austria’s Jews wary of far-right charm offensive, www.timeofisrael.com, 3 de marzo de 2019.
[^16]: Yossi Melman, Sichrovsky Denies He Was a Mossad Agent, www.haaretz.com, 3 de junio de 2005.
[^17]: Fernando Heller, Spagna: il leader di Vox pretende le scuse di Sánchez per aver messo in dubbio l’offensiva israeliana contro Hamas, https://euractiv.it, 6 de diciembre de 2023.
[^18]: El ultraderechista Vox defiende los ataques de Israel en Gaza tras la polémica reunión con Netanyahu, euronews, 29 de mayo de 2024.
[^19]: Bruno Vespa, Vannacci: «Dopo l’Ue tornerei nell’esercito», «La Verità», 30 de octubre de 2024, p. 7.
[^20]: Missione Iraq: Riconoscimento al Generale Roberto Vannacci, en www.difesa.it , cit. en www.wikipedia.org
Artículo original: Hipérbola Janus, Patriots (TOR), 9/Ene/2025
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A Causa
o Princípios de Economia Política de Menger é o único livro que enfatiza a CAUSA o tempo todo. os cientistas todos parecem não saber, ou se esquecer sempre, que as coisas têm causa, e que o conhecimento verdadeiro é o conhecimento da causa das coisas.
a causa é uma categoria metafísica muito superior a qualquer correlação ou resultado de teste de hipótese, ela não pode ser descoberta por nenhum artifício econométrico ou reduzida à simples antecedência temporal estatística. a causa dos fenômenos não pode ser provada cientificamente, mas pode ser conhecida.
o livro de Menger conta para o leitor as causas de vários fenômenos econômicos e as interliga de forma que o mundo caótico da economia parece adquirir uma ordem no momento em que você lê. é uma sensação mágica e indescritível.
quando eu te o recomendei, queria é te imbuir com o espírito da busca pela causa das coisas. depois de ler aquilo, você está apto a perceber continuidade causal nos fenômenos mais complexos da economia atual, enxergar as causas entre toda a ação governamental e as suas várias consequências na vida humana. eu faço isso todos os dias e é a melhor sensação do mundo quando o caos das notícias do caderno de Economia do jornal -- que para o próprio jornalista que as escreveu não têm nenhum sentido (tanto é que ele escreve tudo errado) -- se incluem num sistema ordenado de causas e consequências.
provavelmente eu sempre erro em alguns ou vários pontos, mas ainda assim é maravilhoso. ou então é mais maravilhoso ainda quando eu descubro o erro e reinsiro o acerto naquela racionalização bela da ordem do mundo econômico que é a ordem de Deus.
em scrap para T.P.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A biblioteca infinita
Agora esqueci o nome do conto de Jorge Luis Borges em que a tal biblioteca é descrita, ou seus detalhes específicos. Eu tinha lido o conto e nunca havia percebido que ele matava a questão da aleatoriedade ser capaz de produzir coisas valiosas. Precisei mesmo da Wikipédia me dizer isso.
Alguns anos atrás levantei essa questão para um grupo de amigos sem saber que era uma questão tão batida e baixa. No meu exemplo era um cachorro andando sobre letras desenhadas e não um macaco numa máquina de escrever. A minha conclusão da discussão foi que não importa o que o cachorro escrevesse, sem uma inteligência capaz de compreender aquilo nada passaria de letras aleatórias.
Borges resolve tudo imaginando uma biblioteca que contém tudo o que o cachorro havia escrito durante todo o infinito em que fez o experimento, e portanto contém todo o conhecimento sobre tudo e todas as obras literárias possíveis -- mas entre cada página ou frase muito boa ou pelo menos legívei há toneladas de livros completamente aleatórios e uma pessoa pode passar a vida dentro dessa biblioteca que contém tanto conhecimento importante e mesmo assim não aprender nada porque nunca vai achar os livros certos.
Everything would be in its blind volumes. Everything: the detailed history of the future, Aeschylus' The Egyptians, the exact number of times that the waters of the Ganges have reflected the flight of a falcon, the secret and true nature of Rome, the encyclopedia Novalis would have constructed, my dreams and half-dreams at dawn on August 14, 1934, the proof of Pierre Fermat's theorem, the unwritten chapters of Edwin Drood, those same chapters translated into the language spoken by the Garamantes, the paradoxes Berkeley invented concerning Time but didn't publish, Urizen's books of iron, the premature epiphanies of Stephen Dedalus, which would be meaningless before a cycle of a thousand years, the Gnostic Gospel of Basilides, the song the sirens sang, the complete catalog of the Library, the proof of the inaccuracy of that catalog. Everything: but for every sensible line or accurate fact there would be millions of meaningless cacophonies, verbal farragoes, and babblings. Everything: but all the generations of mankind could pass before the dizzying shelves – shelves that obliterate the day and on which chaos lies – ever reward them with a tolerable page.
Tenho a impressão de que a publicação gigantesca de artigos, posts, livros e tudo o mais está transformando o mundo nessa biblioteca. Há tanta coisa pra ler que é difícil achar o que presta. As pessoas precisam parar de escrever.
-
 @ fe02e8ec:f07fbe0b
2025-03-31 14:43:22
@ fe02e8ec:f07fbe0b
2025-03-31 14:43:22\ Und genau dafür wirst auch du gedrillt werden: Menschen zu jagen und töten. Unbekannte, die auch nicht wissen, was sie hier tun. Oder Unschuldige, die nicht rechtzeitig fliehen konnten. Einfach töten. Alle. Ohne zu fragen. Denn das ist deine Aufgabe, Soldat: Töte Menschen!
Egal, was du vorher warst, Heizungsmonteur, KFZ-Mechaniker, Veganer, Marketing-Manager, Friseur, Verkäufer, Kindergärtner: Es ist egal. Jetzt musst du töten. Denn du hast mitgemacht. Entweder, weil du es nicht ernst genommen hast, weil du dich nie für Politik interessiert hast. Oder weil du gedacht hast, das alles betrifft dich nicht. Weil du gedacht hast, Wahlen könnten etwas verändern. Oder weil du immer das Maul gehalten hast, damit dich keiner als «Rechter» bezeichnet. Egal. Jetzt musst du töten. Das ist das Spiel.
Ja, es ist ein Spiel. Grausam, abartig, menschenverachtend. Dennoch hat es Regeln: Diejenigen, die das Spiel beginnen, müssen niemals selbst auf das Schlachtfeld. Das ist die erste Regel. Ihre Söhne auch nicht, nicht die Söhne der anderen Politiker, nicht die der EU-Abgeordneten, nicht die der Parteibonzen. Auch nicht die der Banker, der Vorstandsvorsitzenden, der Chefredakteure. Denn alle wissen, wie man das Spiel spielt. Nur du nicht.
Du bist einfach eine Figur auf dem Spielfeld, die es verpasst hat, NEIN zu sagen, als noch Gelegenheit war. Jetzt bist du verwandelt worden in eine menschliche Drohne. Wenn sie sagen: töte!, dann tötest du. Denken kannst du, wenn alles vorbei ist. Falls du je wieder nach Hause kommst. Vielleicht sogar mit beiden Beinen und beiden Armen. Vielleicht auch nicht. Egal. Wer hätte Mitleid mit einer Spielfigur?
Nein, du musst töten. Das ist deine Aufgabe. Sie sagen es nun schon seit Monaten, warum glaubst du es nicht? Sie meinen es ernst. Wenn du den Brief in Händen hältst ist es zu spät. Es gilt dann das Notstandsrecht und keiner kann mehr verweigern. Da hättest du dich vorher drum kümmern müssen. Oder auf eine Demo gehen. Oder laut und mit klarer Stimme in jedem Gespräch den Wahnsinn anprangern. Hast du aber nicht.
Jetzt musst du töten oder du wirst getötet. Das ist das Spiel. Du hättest selbst denken können. Hast du aber nicht. Hast deine Zeit mit sinnlosen Videos vertan, Netflix geguckt und hast Influencerinnen geliked. Die müssen nicht an die Front. Aber du. Morgen, wenn du aufstehst, die Uniform anziehst und rausgehst, dann wirst du Befehle ausführen oder erschossen werden. Also wirst du Menschen töten. Dein Leben wird nie wieder so sein, wie zuvor. Dein Schmerz, deine Schuld, dein Leid: sie gehen ein in die unendliche Reihe der Soldaten, die seit Jahrhunderten dasselbe Schicksal erlitten. Deren Schreie noch immer durch den ewigen Raum hallen. Deren Opfer von den Herren des Spiels mit einem Lächeln entgegengenommen wurde. Deren Gliedmaßen auf den Schlachtfeldern liegen geblieben waren. Zum Dank erhielten sie eine Medaille. Ein Stück Blech für den rechten Arm, einen Grabstein für den Vater, den Bruder, den Sohn. Für das Vaterland. Für Europa. Für die Demokratie. Der Hohn tropft aus jedem Politikerwort, doch die Menschen glauben noch immer die uralte Geschichte von Freund und Feind, von Gut und Böse.

\ Wer nicht aufwachen will muss töten. Du. Nicht am Bildschirm. In der echten Welt. Wo man nicht auf Replay drücken kann. Wo man den Gegner nicht nach links oder rechts swipen kann, denn er ist echt, real, lebendig. Noch. Entweder er oder du. Jetzt ist es zu spät für Entscheidungen. Kannst du es spüren? Die Work-Life Balance wird zur Kill-or-be-Killed balance. Es gibt kein Entrinnen. Denn du hast mitgemacht. Schweigen ist Zustimmung. Sich-nicht-drumkümmern ist Zustimmung. Kriegsparteien zu wählen ist noch mehr Zustimmung.
Heute.
Heute lässt sich noch etwas ändern.
Es hat nichts zu tun mit rechts oder links. Nur mit Menschlichkeit versus Hass, Macht und dem ganz großen Geld. Das sind die Gründe, für die du töten oder sterben musst.
Wie entscheidest du dich?
-
 @ b4403b24:83542d4e
2025-03-31 14:31:53
@ b4403b24:83542d4e
2025-03-31 14:31:53🚀 Bitcoin Enthusiasts! Tomorrow the price of #BTCPrague2025 tickets goes up so take advantage of the 10% discount using code from the video - BTCBULGARIA.
✅ Network with leaders ✅ Learn blockchain strategies ✅ Gain crypto insights
Secure your spot NOW!
Bitcoin #BTC #BTCPrague
originally posted at https://stacker.news/items/930210
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28IPFS problems: Shitcoinery
IPFS was advertised to the Ethereum community since the beggining as a way to "store" data for their "dApps". I don't think this is harmful in any way, but for some reason it may have led IPFS developers to focus too much on Ethereum stuff. Once I watched a talk showing libp2p developers – despite being ignored by the Ethereum team (that ended up creating their own agnostic p2p library) – dedicating an enourmous amount of work on getting a libp2p app running in the browser talking to a normal Ethereum node.
The always somewhat-abandoned "Awesome IPFS" site is a big repository of "dApps", some of which don't even have their landing page up anymore, useless Ethereum smart contracts that for some reason use IPFS to store whatever the useless data their users produce.
Again, per se it isn't a problem that Ethereum people are using IPFS, but it is at least confusing, maybe misleading, that when you search for IPFS most of the use-cases are actually Ethereum useless-cases.
See also
- Bitcoin, the only non-shitcoin
-
 @ 9dd283b1:cf9b6beb
2025-03-31 13:21:08
@ 9dd283b1:cf9b6beb
2025-03-31 13:21:08Do you still feel anxiety when Bitcoin's price drops significantly, even though you're in fiat profit (100% +) ? Why or why not? And when did you truly stop feeling any emotional attachment to the price fluctuations?
originally posted at https://stacker.news/items/930139
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Why IPFS cannot work, again
Imagine someone comes up with a solution for P2P content-addressed data-sharing that involves storing all the files' contents in all computers of the network. That wouldn't work, right? Too much data, if you think this can work then you're a BSV enthusiast.
Then someone comes up with the idea of not storing everything in all computers, but only some things on some computers, based on some algorithm to determine what data a node would store given its pubkey or something like that. Still wouldn't work, right? Still too much data no matter how much you spread it, but mostly incentives not aligned, would implode in the first day.
Now imagine someone says they will do the same thing, but instead of storing the full contents each node would only store a pointer to where each data is actually available. Does that make it better? Hardly so. Still, you're just moving the problem.
This is IPFS.
Now you have less data on each computer, but on a global scale that is still a lot of data.
No incentives.
And now you have the problem of finding the data. First if you have some data you want the world to access you have to broadcast information about that, flooding the network -- and everybody has to keep doing this continuously for every single file (or shard of file) that is available.
And then whenever someone wants some data they must find the people who know about that, which means they will flood the network with requests that get passed from peer to peer until they get to the correct peer.
The more you force each peer to store the worse it becomes to run a node and to store data on behalf of others -- but the less your force each peer to store the more flooding you'll have on the global network, and the slower will be for anyone to actually get any file.
But if everybody just saves everything to Infura or Cloudflare then it works, magic decentralized technology.
Related
-
 @ 866e0139:6a9334e5
2025-03-31 12:44:27
@ 866e0139:6a9334e5
2025-03-31 12:44:27
Autor: Carlos A. Gebauer. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Am 18. März 1924 schenkte meine Großmutter ihren Töchtern einen kleinen Bruder. Weil sein Vater fürchtete, der Junge könnte unter seinen vier Schwestern verweichlichen, schickte er den Kleinen zu Wochenendfreizeiten einer örtlichen Pfadfindergruppe. Ein Weltkriegsveteran veranstaltete dort mit den Kindern Geländespiele quer durch die schlesischen Wälder. Man lernte, Essbares zu finden, Pilze zu bestimmen, sich im Freien zu orientieren und Feuer zu machen.
Bald wurde deutlich, dass der Heranwachsende auch nicht mehr in den Blockflötenkreis seiner Schwestern und ihrer Freundinnen passte. Das Umfeld befürwortete, sein besonderes musikalisches Talent auf das Klavierspiel und das Flügelhorn zu richten. Kontakte bei der anschließenden Kirchenmusik mündeten schließlich in den elterlichen Entschluss, den nun 14-jährigen in ein Musikschulinternat zu schicken.
Es begann der Zweite Weltkrieg
Ein Jahr später, das erste Heimweh hatte sich langsam beruhigt, änderten sich die Verhältnisse schlagartig. Es begann der Zweite Weltkrieg. Mitschüler unter den jungen Musikern erfuhren, dass ihre älteren Brüder nun Soldaten werden mussten. Noch hielt sich die Gemeinschaft der jetzt 15-jährigen im Internat aber an einer Hoffnung fest: Bis sie selbst in das wehrfähige Alter kommen würden, müsste der Krieg längst beendet sein. In dieser Stimmungslage setzten sie ihre Ausbildung fort.
Es kam anders. Für den 18-jährigen erfolgte die befürchtete Einberufung in Form des „Gestellungsbefehls“. Entsprechend seiner Fähigkeiten sah man ihn zunächst für ein Musikkorps vor und schickte ihn zu einer ersten Grundausbildung nach Südfrankreich. Bei Nizza fand er sich nun plötzlich zwischen Soldaten, die Handgranaten in das Mittelmeer warfen, um Fische zu fangen. Es war das erste Mal, dass er fürchtete, infolge Explosionslärms sein Gehör zu verlieren. In den kommenden Jahren sollte er oft die Ohren zu- und den Mund offenhalten müssen, um sich wenigstens die Möglichkeit der angezielten Berufsausübung zu erhalten – wenn es überhaupt je dazu kommen würde.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Schon nach kurzer Zeit änderte sich die Befehlslage wieder. Der Musikstudent wurde nun zum Infanteristen und nach Russland an die Front verbracht. Vor ihm lagen jetzt drei Kriegsjahre: Gewalt, Dreck, Gewehrkugeln, Panzerschlachten, Granatsplitter, Luftangriffe, Entbehrungen, Hunger, Kälte, sieben Verwundungen, Blut und Schmerzen, Sterbende überall, Tote, Schreiende. Verzweiflung. Sorgen. Ängste. Todesangst. Zurückweichen? Verboten! Und die stets klare Ansage dazu: Wer nicht da vorne gegen den Feind um sein Leben kämpft, dem wird es ganz sicher da hinten von den eigenen Kameraden genommen.
Ein gewährter Fronturlaub 1944 versprach glückliche Momente. Zurück zu den Eltern, zurück zu den Schwestern, zurück nach Freiburg. Doch die Familie war nicht zu Hause, die Türen verschlossen. Eine Nachbarin öffnete ihr Fenster und rief dem Ratlosen zu: „Beeil‘ dich! Renn‘ zum Friedhof. Der Vater ist tot. Sie sind alle bei der Beerdigung!“ Wieder hieß es, qualvoll Abschied nehmen. Zurück an die Front.
Nach einem weiteren russischen Winter brach sich unübersehbar die Erkenntnis Bahn, dass der Krieg nun seinem Ende zugehe. Doch das Bemühen im Rückzug, sich mit einem versprengten Haufen irgendwie Richtung Heimat orientieren zu können, wurde doppelt jäh unterbrochen. Fanatische Vorgesetzte befahlen die längst Geschlagenen wieder gen Osten. Kurz darauf fielen sie heranrückenden russischen Truppen in die Hände.
Kriegsgefangenschaft: Tabakration gegen Brot
Drei Jahre dem Tod entgangen, schwer verletzt und erschöpft war der 21-jährige also nun ein Kriegsgefangener. Jetzt lagen drei Jahre russischer Kriegsgefangenschaft vor ihm. Ständig war unklar, wie es weiterginge. Unmöglich jedenfalls, sich noch wie ein Pfadfinder aus den Wäldern zu ernähren. Es begannen die Jahre des Schlafens auf Brettern, die Zeit der ziellosen Zugtransporte an unbekannte Orte. Niemand sprach. Nur der Sonnenstand machte klar: Es ging nie Richtung Heimat, sondern immer weiter nach Osten. Weil der Blechbläser nicht rauchte, konnte er seine Tabakration gegen Brot tauschen. So überlebte er auch die Zeit des Hungers und der Morde in den Lagern, die Horrorbilder der nachts Erschlagenen und in die Latrinen geworfenen Toten, der sinnlosen Zwangsarbeiten und der allgegenwärtigen Wanzen. Wer versuchte zu fliehen, der wurde erschossen und sein Körper zur Abschreckung in den Fangdrähten belassen. Im Sommer stanken die dort verwesenden Leichen, wenn nicht Vögel sie rechtzeitig gefressen hatten.
Als der 24-jährige schließlich sechs Jahre nach seiner Einberufung aus russischer Kriegsgefangenschaft entlassen wurde, gab es kein Zurück mehr in seine schlesische Heimat. Abgemagert reiste er der vertriebenen Mutter nach, die mit seinen Schwestern und Millionen anderen Flüchtlingen im Westen Deutschlands verteilt worden war. Kraft Ordnungsverfügung wohnte sie jetzt im sauerländischen Bad Laasphe in einem schimmligen Garagenanbau. Als ihn ein Passant auf dieser Reise morgens allein, nur mit einem Becher an der Schnur um den Hals, auf Krücken durch Berlin ziehen sah, gab er ihm schweigend sein Butterbrot.
Der kleine, sanfte Junge aus dem schlesischen Freiburg hat danach noch 60 Jahre gelebt. Es dauerte zunächst sechs Jahre, bis er wieder kräftig genug war, ein Instrument zu spielen. 30-jährig saß er dann endlich in einem Orchester und begann ein normales Berufsleben. Aber sein Körper und seine Seele waren für immer aus jeder Normalität gerissen.
Irgendwo in Russland war ihm die linke Hüfte so versteift worden, dass sich seine Beine im Liegen an Wade und Schienbein überkreuzten. Er musste also stets den Oberkörper vorbeugen, um überhaupt laufen zu können. Über die Jahrzehnte verzog sich so sein gesamter Knochenbau. Jeder Tag brachte neue orthopädische Probleme und Schmerzen. Ärzte, Masseure, Physiotherapeuten, Schmerzmittel und Spezialausrüstungen aller Art prägten die Tagesabläufe. Asymmetrisch standen seine Schuhe nebeneinander, die ein Spezialschuster ihm mit erhöhter Sohle und Seitenstabilisierung am Knöchel fertigte. Sessel oder Sofas waren ihm nicht nutzbar, da er nur auf einem Spezialstuhl mit halb abgesenkter Sitzfläche Ruhe fand. Auf fremden Stühlen konnte er nur deren Vorderkante nutzen.
In den Nächten schrie er im Schlaf
Und auch wenn er sich ohne Krankheitstage bis zuletzt durch seinen Berufsalltag kämpfte, so gab es doch viele Tage voller entsetzlicher Schmerzen, wenn sich seine verdrehte Wirbelsäule zur Migräne in den Kopf bohrte. Bei alledem hörte man ihn allerdings niemals über sein Schicksal klagen. Er ertrug den ganzen Wahnsinn mit einer unbeschreiblichen Duldsamkeit. Nur in den Nächten schrie er bisweilen im Schlaf. In einem seiner Alpträume fürchtete er, Menschen getötet zu haben. Aber auch das erzählte er jahrzehntelang einzig seiner Frau.
Als sich einige Jahre vor seinem Tod der orthopädische Zustand weiter verschlechterte, konsultierte er einen Operateur, um Entlastungsmöglichkeiten zu erörtern. Der legte ihn auf eine Untersuchungsliege und empfahl, Verbesserungsversuche zu unterlassen, weil sie die Lage allenfalls verschlechtern konnten. In dem Moment, als er sich von der Liege erheben sollte, wurde deutlich, dass ihm dies nicht gelang. Die gereichte Hand, um ihn hochzuziehen, ignorierte er. Stattdessen rieb er seinen Rumpf ganz alleine eine quälend lange Minute über die Fläche, bis er endlich einen Winkel fand, um sich selbst in die Senkrechte zu bugsieren. Sich nicht auf andere verlassen, war sein Überlebenskonzept. Jahre später, als sich sein Zustand noch weiter verschlechtert hatte, lächelte er über seine Behinderung: „Ich hätte schon vor 60 Jahren tot auf einem Acker in Russland liegen können.“ Alles gehe irgendwann vorbei, tröstete er sich. Das war das andere Überlebenskonzept: liebevoll, friedfertig und sanft anderen gegenüber, unerbittlich mit sich selbst.
Sechs Monate vor seinem Tod saß er morgens regungslos auf seinem Spezialstuhl. Eine Altenpflegerin fand ihn und schlug Alarm. Mit allen Kunstgriffen der medizinischen Technik wurde er noch einmal in das Leben zurückkatapultiert. Aber seine Kräfte waren erschöpft. Es schob sich das Grauen der Vergangenheit zwischen ihn und die Welt. Bettlägerig kreiste er um sich selbst, erkannte niemanden und starrte mit weit offenen Augen an die Decke. „Die Russen schmeißen wieder Brandbomben!“, war einer seiner letzten Sätze.
Der kleine Junge aus Schlesien ist nicht zu weich geraten. Er hat sein Leid mit unbeugsamer Duldsamkeit ertragen. Er trug es wohl als Strafe für das Leid, das er anderen anzutun genötigt worden war. An seinem Geburtstag blühen immer die Magnolien. In diesem Jahr zum hundertsten Mal.
Dieser Text wurde am 23.3.2024 erstveröffentlicht auf „eigentümlich frei“.
Carlos A. Gebauer studierte Philosophie, Neuere Geschichte, Sprach-, Rechts- und Musikwissenschaften in Düsseldorf, Bayreuth und Bonn. Sein juristisches Referendariat absolvierte er in Düsseldorf, u.a. mit Wahlstationen bei der Landesrundfunkanstalt NRW, bei der Spezialkammer für Kassenarztrecht des Sozialgerichtes Düsseldorf und bei dem Gnadenbeauftragten der Staatsanwaltschaft Düsseldorf.
Er war unter anderem als Rechtsanwalt und Notarvertreter bis er im November 2003 vom nordrhein-westfälischen Justizministerium zum Richter am Anwaltsgericht für den Bezirk der Rechtsanwaltskammer Düsseldorf ernannt wurde. Seit April 2012 arbeitet er in der Düsseldorfer Rechtsanwaltskanzlei Lindenau, Prior & Partner. Im Juni 2015 wählte ihn die Friedrich-August-von-Hayek-Gesellschaft zu ihrem Stellvertretenden Vorsitzenden. Seit Dezember 2015 ist er Richter im Zweiten Senat des Anwaltsgerichtshofes NRW.
1995 hatte er parallel zu seiner anwaltlichen Tätigkeit mit dem Verfassen gesellschaftspolitischer und juristischer Texte begonnen. Diese erschienen seither unter anderem in der Neuen Juristischen Wochenschrift (NJW), der Zeitschrift für Rechtspolitik (ZRP) in der Frankfurter Allgemeinen Zeitung, der Freien Presse Chemnitz, dem „Schweizer Monat“ oder dem Magazin für politische Kultur CICERO. Seit dem Jahr 2005 ist Gebauer ständiger Kolumnist und Autor des Magazins „eigentümlich frei“.
Gebauer glaubt als puristischer Liberaler unverbrüchlich an die sittliche Verpflichtung eines jeden einzelnen, sein Leben für sich selbst und für seine Mitmenschen verantwortlich zu gestalten; jede Fremdbestimmung durch Gesetze, staatliche Verwaltung, politischen Einfluss oder sonstige Gewalteinwirkung hat sich demnach auf ein ethisch vertretbares Minimum zu beschränken. Die Vorstellung eines europäischen Bundesstaates mit zentral detailsteuernder, supranationaler Staatsgewalt hält er für absurd und verfassungswidrig.
\ Aktuelle Bücher:
Hayeks Warnung vor der Knechtschaft (2024) – hier im Handel
Das Prinzip Verantwortungslosigkeit (2023) – hier im Handel
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 65038d69:1fff8852
2025-03-31 12:13:39
@ 65038d69:1fff8852
2025-03-31 12:13:39Artificial intelligence is upon us and not showing any signs of slowing. The most common concern from those in the workforce is being replaced by one of these “thinking machines”. But what if AI wasn’t coming for your job? What if it was coming for your boss’s job instead?
I happened across the following post on X: https://x.com/BrianRoemmele/status/1905754986795151629 Brian describes having installed an AI system that provides an omniscient “shadow” to each of the executives at a client company, which can then be queried by the CEO for reports. The CEO seems to like it so far, and if it leads to less time spent writing internal reports I’m sure the executives like it too. But many of you may be recoiling at the thought of an always-on nanycam who’s sole purpose seems to be to snitch on you to your boss, and judging by the replies to Brian’s post, you’re not alone. If your supervisor has a history of targeting you your fears may not be misplaced. Workplace surveillance tools are often coyly marketed for this.
What if instead of your boss using an AI tool to spy on you, your boss was completely replaced by an AI? Would your supervisor having no biases or favouritism sway your opinion? What about being able to tailor its communication specifically to you? Expressing no judgement at your clarifying questions? Being immediately available 24/7? Perfectly equitable expectations and performance reviews? Just writing that almost has me convinced this would usher in a workplace utopia.
In practice guaranteeing zero bias is extremely difficult. After all, these things are programmed by humans and learn from human data. Their “weights” could also be intentionally adjusted to favour or target. If the AI’s supervisor follows the Pareto Principle (also known as the 80/20 Rule) they may be tempted to ask it for a list of the lowest performing employees to be laid off on a regular basis. Not keeping yourself in the top 20% of performers (by whatever metrics the AI has been programmed to look for) may mean your job. The dystopian-future videogame “Cyberpunk 2077” tells a story of a company that brings in an AI only to have it fire all the human workers in favour of automation and copies of itself. Clearly it’s implementers forgot to set hard limits on its executive powers. The shareholders were happy with all-time high profits though…
When technology is blamed for these sorts of existential problems the IT industry collectively sighs and repeats the mantra, “The problem is not the technology. The problem is the people.” A quote from a 1979 IBM presentation is likewise summoned; “A computer can never be held accountable, therefore a computer must never make a management decision.” As a darker example, the Nuremberg trials post-WWII saw the precedent set that acting under “superior orders” is not a valid defence for war crimes or crimes against humanity. It seems responsibility can’t be passed to others, whether man or machine. The endless task of generating reports and presentations can probably be automated away though.
Would you work under an AI, or “hire” an AI to manage others? We can help you with that; you can find us at scalebright.ca.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Who will build the roads?
Who will build the roads? Em Lagoa Santa, as mais novas e melhores ruas -- que na verdade acabam por formar enormes teias de bairros que se interligam -- são construídas pelos loteadores que querem as ruas para que seus lotes valham mais -- e querem que outras pessoas usem as ruas também. Também são esses mesmos loteadores que colocam os postes de luz e os encanamentos de água, não sem antes terem que se submeter a extorsões de praxe praticadas por COPASA e CEMIG.
Se ao abrir um loteamento, condomínio, prédio um indivíduo ou uma empresa consegue sem muito problema passar rua, eletricidade, água e esgoto, por que não seria possível existir livre-concorrência nesses mercados? Mesmo aquela velha estória de que é ineficiente passar cabos de luz duplicados para que companhias elétricas possam competir já me parece bobagem.
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28How IPFS is broken
I once fell for this talk about "content-addressing". It sounds very nice. You know a certain file exists, you know there are probably people who have it, but you don't know where or if it is hosted on a domain somewhere. With content-addressing you can just say "start" and the download will start. You don't have to care.
Other magic properties that address common frustrations: webpages don't go offline, links don't break, valuable content always finds its way, other people will distribute your website for you, any content can be transmitted easily to people near you without anyone having to rely on third-party centralized servers.
But you know what? Saying a thing is good doesn't automatically make it possible and working. For example: saying stuff is addressed by their content doesn't change the fact that the internet is "location-addressed" and you still have to know where peers that have the data you want are and connect to them.
And what is the solution for that? A DHT!
DHT?
Turns out DHTs have terrible incentive structure (as you would expect, no one wants to hold and serve data they don't care about to others for free) and the IPFS experience proves it doesn't work even in a small network like the IPFS of today.
If you have run an IPFS client you'll notice how much it clogs your computer. Or maybe you don't, if you are very rich and have a really powerful computer, but still, it's not something suitable to be run on the entire world, and on web pages, and servers, and mobile devices. I imagine there may be a lot of unoptimized code and technical debt responsible for these and other problems, but the DHT is certainly the biggest part of it. IPFS can open up to 1000 connections by default and suck up all your bandwidth -- and that's just for exchanging keys with other DHT peers.
Even if you're in the "client" mode and limit your connections you'll still get overwhelmed by connections that do stuff I don't understand -- and it makes no sense to run an IPFS node as a client, that defeats the entire purpose of making every person host files they have and content-addressability in general, centralizes the network and brings back the dichotomy client/server that IPFS was created to replace.
Connections?
So, DHTs are a fatal flaw for a network that plans to be big and interplanetary. But that's not the only problem.
Finding content on IPFS is the most slow experience ever and for some reason I don't understand downloading is even slower. Even if you are in the same LAN of another machine that has the content you need it will still take hours to download some small file you would do in seconds with
scp-- that's considering that IPFS managed to find the other machine, otherwise your command will just be stuck for days.Now even if you ignore that IPFS objects should be content-addressable and not location-addressable and, knowing which peer has the content you want, you go there and explicitly tell IPFS to connect to the peer directly, maybe you can get some seconds of (slow) download, but then IPFS will drop the connection and the download will stop. Sometimes -- but not always -- it helps to add the peer address to your bootstrap nodes list (but notice this isn't something you should be doing at all).
IPFS Apps?
Now consider the kind of marketing IPFS does: it tells people to build "apps" on IPFS. It sponsors "databases" on top of IPFS. It basically advertises itself as a place where developers can just connect their apps to and all users will automatically be connected to each other, data will be saved somewhere between them all and immediately available, everything will work in a peer-to-peer manner.
Except it doesn't work that way at all. "libp2p", the IPFS library for connecting people, is broken and is rewritten every 6 months, but they keep their beautiful landing pages that say everything works magically and you can just plug it in. I'm not saying they should have everything perfect, but at least they should be honest about what they truly have in place.
It's impossible to connect to other people, after years there's no js-ipfs and go-ipfs interoperability (and yet they advertise there will be python-ipfs, haskell-ipfs, whoknowswhat-ipfs), connections get dropped and many other problems.
So basically all IPFS "apps" out there are just apps that want to connect two peers but can't do it manually because browsers and the IPv4/NAT network don't provide easy ways to do it and WebRTC is hard and requires servers. They have nothing to do with "content-addressing" anything, they are not trying to build "a forest of merkle trees" nor to distribute or archive content so it can be accessed by all. I don't understand why IPFS has changed its core message to this "full-stack p2p network" thing instead of the basic content-addressable idea.
IPNS?
And what about the database stuff? How can you "content-address" a database with values that are supposed to change? Their approach is to just save all values, past and present, and then use new DHT entries to communicate what are the newest value. This is the IPNS thing.
Apparently just after coming up with the idea of content-addressability IPFS folks realized this would never be able to replace the normal internet as no one would even know what kinds of content existed or when some content was updated -- and they didn't want to coexist with the normal internet, they wanted to replace it all because this message is more bold and gets more funding, maybe?
So they invented IPNS, the name system that introduces location-addressability back into the system that was supposed to be only content-addressable.
And how do they manage to do it? Again, DHTs. And does it work? Not really. It's limited, slow, much slower than normal content-addressing fetches, most of the times it doesn't even work after hours. But still although developers will tell it is not working yet the IPFS marketing will talk about it as if it was a thing.
Archiving content?
The main use case I had for IPFS was to store content that I personally cared about and that other people might care too, like old articles from dead websites, and videos, sometimes entire websites before they're taken down.
So I did that. Over many months I've archived stuff on IPFS. The IPFS API and CLI don't make it easy to track where stuff are. The
pincommand doesn't help as it just throws your pinned hash in a sea of hashes and subhashes and you're never able to find again what you have pinned.The IPFS daemon has a fake filesystem that is half-baked in functionality but allows you to locally address things by names in a tree structure. Very hard to update or add new things to it, but still doable. It allows you to give names to hashes, basically. I even began to write a wrapper for it, but suddenly after many weeks of careful content curation and distribution all my entries in the fake filesystem were gone.
Despite not having lost any of the files I did lose everything, as I couldn't find them in the sea of hashes I had in my own computer. After some digging and help from IPFS developers I managed to recover a part of it, but it involved hacks. My things vanished because of a bug at the fake filesystem. The bug was fixed, but soon after I experienced a similar (new) bug. After that I even tried to build a service for hash archival and discovery, but as all the problems listed above began to pile up I eventually gave up. There were also problems of content canonicalization, the code the IPFS daemon use to serve default HTML content over HTTP, problems with the IPFS browser extension and others.
Future-proof?
One of the core advertised features of IPFS was that it made content future-proof. I'm not sure they used this expression, but basically you have content, you hash that, you get an address that never expires for that content, now everybody can refer to the same thing by the same name. Actually, it's better: content is split and hashed in a merkle-tree, so there's fine-grained deduplication, people can store only chunks of files and when a file is to be downloaded lots of people can serve it at the same time, like torrents.
But then come the protocol upgrades. IPFS has used different kinds of hashing algorithms, different ways to format the hashes, and will change the default algorithm for building the merkle-trees, so basically the same content now has a gigantic number of possible names/addresses, which defeats the entire purpose, and yes, files hashed using different strategies aren't automagically compatible.
Actually, the merkle algorithm could have been changed by each person on a file-by-file basis since the beginning (you could for example split a book file by chapter or page instead of by chunks of bytes) -- although probably no one ever did that. I know it's not easy to come up with the perfect hashing strategy in the first go, but the way these matters are being approached make me wonder that IPFS promoters aren't really worried about future-proof, or maybe we're just in Beta phase forever.
Ethereum?
This is also a big problem. IPFS is built by Ethereum enthusiasts. I can't read the mind of people behind IPFS, but I would imagine they have a poor understanding of incentives like the Ethereum people, and they tend towards scammer-like behavior like getting a ton of funds for investors in exchange for promises they don't know they can fulfill (like Filecoin and IPFS itself) based on half-truths, changing stuff in the middle of the road because some top-managers decided they wanted to change (move fast and break things) and squatting fancy names like "distributed web".
The way they market IPFS (which is not the main thing IPFS was initially designed to do) as a "peer-to-peer cloud" is very seductive for Ethereum developers just like Ethereum itself is: as a place somewhere that will run your code for you so you don't have to host a server or have any responsibility, and then Infura will serve the content to everybody. In the same vein, Infura is also hosting and serving IPFS content for Ethereum developers these days for free. Ironically, just like the Ethereum hoax peer-to-peer money, IPFS peer-to-peer network may begin to work better for end users as things get more and more centralized.
More about IPFS problems:
- IPFS problems: Too much immutability
- IPFS problems: General confusion
- IPFS problems: Shitcoinery
- IPFS problems: Community
- IPFS problems: Pinning
- IPFS problems: Conceit
- IPFS problems: Inefficiency
- IPFS problems: Dynamic links
See also
- A crappy course on torrents, on the protocol that has done most things right
- The Tragedy of IPFS in a series of links, an ongoing Twitter thread.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Lagoa Santa: como chegar -- partindo da rodoviária de Belo Horizonte
Ao descer de seu ônibus na rodoviária de Belo Horizonte às 4 e pouco da manhã, darás de frente para um caubói que toma cerveja em seus trajes típicos em um bar no setor mesmo de desembarque. Suba a escada à direita que dá no estacionamento da rodoviária. Vire à esquerda e caminhe por mais ou menos 400 metros, atravessando uma área onde pessoas suspeitas -- mas provavelmente dormindo em pé -- lhe observam, e então uma pracinha ocupada por um clã de mendigos. Ao avistar um enorme obelisco no meio de um cruzamento de duas avenidas, vire à esquerda e caminhe por mais 400 metros. Você verá uma enorme, antiga e bela estação com uma praça em frente, com belas fontes aqüáticas. Corra dali e dirija-se a um pedaço de rua à direita dessa praça. Um velho palco de antigos carnavais estará colocado mais ou menos no meio da simpática ruazinha de parelepípedos: é onde você pegará seu próximo ônibus.
Para entrar na estação é necessário ter um cartão com créditos recarregáveis. Um viajante prudente deixa sempre um pouco de créditos em seu cartão a fim de evitar filas e outros problemas de indisponibilidade quando chega cansado de viagem, com pressa ou em horários incomuns. Esse tipo de pessoa perceberá que foi totalmente ludibriado ao perceber que que os créditos do seu cartão, abastecido quando de sua última vinda a Belo Horizonte, há três meses, pereceram de prazo de validade e foram absorvidos pelos cofre públicos. Terá, portanto, que comprar mais créditos. O guichê onde os cartões são abastecidos abre às 5h, mas não se espante caso ele não tenha sido aberto ainda quando o primeiro ônibus chegar, às 5h10.
Com alguma sorte, um jovem de moletom, autorizado por dois ou três fiscais do sistema de ônibus que conversam alegremente, será o operador da catraca. Ele deixa entrar sem pagar os bêbados, os malandros, os pivetes. Bastante empático e perceptivo do desespero dos outros, esse bom rapaz provavelmente também lhe deixará entrar sem pagar.
Uma vez dentro do ônibus, não se intimide com os gritalhões e valentões que, ofendidíssimos com o motorista por ele ter parado nas estações, depois dos ônibus anteriores terem ignorado esses excelsos passageiros que nelas aguardavam, vão aos berros tirar satisfação.
O ponto final do ônibus, 40 minutos depois, é o terminal Morro Alto. Lá você verá, se procurar bem entre vários ônibus e pessoas que despertam a sua mais honesta suspeita, um veículo escuro, apagado, numerado 5882 e que abrigará em seu interior um motorista e um cobrador que descansam o sono dos justos.
Aguarde na porta por mais uns vinte minutos até que, repentinamente desperto, o motorista ligue o ônibus, abra as portas e já comece, de leve, a arrancar. Entre correndo, mas espere mais um tempo, enquanto as pessoas que têm o cartão carregado passem e peguem os melhores lugares, até que o cobrador acorde e resolva te cobrar a passagem nesse velho meio de pagamento, outrora o mais líqüído, o dinheiro.
Este último ônibus deverá levar-lhe, enfim, a Lagoa Santa.
-
 @ 0d1702d6:8f1ac66f
2025-03-31 10:45:57
@ 0d1702d6:8f1ac66f
2025-03-31 10:45:57Als Verrücktheit bezeichnen \ wir die chronische Entwicklung \ eines dauernden Wahnsystems \ bei vollkommener Erhaltung \ der Besonnenheit.
Psychiater Emil Kraepelin 1893
Es ist Teil des westlichen Wahnsystems anzunehmen, Russland habe aus imperialen Absichten heraus 2022 mit nur 130.000 Soldaten die Grenze zur Ukraine überschritten, um so die gesamte Ukraine und später wohlmöglich Westeuropa militärisch einzunehmen, wie z.B. der deutsche Kriegsminister Pistorius seit 2023 suggerierte.
Nachdem die USA bereits 2014 die berechtigten Anti-Korruptions-Proteste der Ukrainer auf dem Maidan durch massive Unterstützung für einen illegalen Putsch gegen die russlandfreundliche Regierung im Sinne des von den USA gewünschten Regimewechsels manipuliert hatten, rüsteten sie in den folgenden Jahren die Ukraine massiv auf, trainierten ihre Soldaten, bauten mehr als einen Stützpunkt und machten die zwischen Ost & West hin- und hergerissene Ukraine so zielgerichtet unterhalb offizieller NATO-Mitgliedschaft schon zu einem kampfstarken eng befreundeten Partner, dessen Krieg gegen seine eigene russisch-stämmige Bevölkerung im rohstoffreichen Donbass die NATO unter Führung der USA somit auch direkt und indirekt unterstützte.
Nachdem der Westen den Russen bei der Wiedervereinigung Deutschlands versprochen hatte, die NATO keinen Zentimeter nach Osten vorzuschieben und stattdessen ein gemeinsames europäisches Sicherheits-System unter Einbeziehung Russlands gemeinsam zu entwickeln, brachen wir diese Zusicherung mit den NATO-Osterweiterungen ab 1999 mehrfach bis heute.
Russland zeigte sich bei seiner zunehmenden Umzingelung durch NATO-Staaten wesentlich nachsichtiger als es umgekehrt die USA schon bei russischen wenigen Raketen auf Kuba 1962 jemals waren und heute sein würden!
Zugleich hatte Russland seit Beginn der NATO-Osterweiterung immer unmissverständlich klar gemacht, dass es eine Stationierung von NATO-Truppen & Raketen in der Ukraine niemals tolerieren würde. Der damalige US-Senator und 2022 US-Präsident Biden sagte schon Ende der 90'er Jahre öffentlich, man werde auf diesen Wunsch der – nach Meinung von US-Geostrategen viel zu schwächen – Russen keine Rücksicht nehmen und erwarte, dass ihnen irgendwann die Nerven ob dieser provokativen Umzingelung durchgingen…
Folgerichtig simulierten die USA und die Europäer - wie Angela Merkel bereits öffentlich eingestanden - nur Verhandlungen über die Abkommen Minsk I und II, damit genügend Zeit blieb die Ukraine aufzurüsten und diese dann einen starken militärischen Schlag gegen die russisch stämmige Bevölkerung im Donbass und die russischen Soldaten auf der Krim ausführen konnte, ein Szenario, welches Anfang 2022 durch einen Truppenaufmarsch auch auf ukrainischer Seite weit fortgeschritten vorbereitet war, bevor im Februar 2022 die russische Armee die Grenze zur Ukraine überschritt.\ \ Trotz alledem kamen schon im April 2022 Unterhändler der Ukraine und Russlands in Ankara zur Übereinkunft eines Waffenstillstandes und Friedensplans (!), der dann allerdings von dem damaligen britischen Premierminister Boris Johnson – in Kooperation mit Joe Biden – durch einen Besuch in Kiew mit dem Versprechen von grenzenlosen Waffenlieferungen \ & logistischer Unterstützung durch die USA und Westeuropa „abgetrieben“ wurde.\ \ Zunächst wurden diese Tatsachen wie üblich öffentlich in deutschen und europäischen Medien als „Verschwörungstheorie“ diffamiert, bis sie in den folgenden Monaten jedoch langsam selbst in die Mainstream-Medien Deutschlands, Europas wie den USA einsickerten.\ \ Zwischenfazit:\ Nachdem die USA ihre so und so viel gewählte globale „Regime Change“ Operation auf dem Maidan schon 10 Jahre lang vorbereitet hatten, gelang ihnen im Jahr 2014 tatsächlich zunächst einen pro-westlichen illegalen Putschpräsidenten, danach auch weitere pro-westliche Präsidenten zu installieren und einem Teil der Weltöffentlichkeit, vor allem aber ihren „Freunden“ im Westen einzureden, die „bösen Russen“ hätten diesen Krieg quasi aus dem Nichts heraus (ohne lange Vorgeschichte!) und trotz Verhandlungen (welche realen statt nur simulierten Verhandlungen?) vom Zaun gebrochen...\ \ Damit war ihr seit über 30 Jahren offen formuliertes geostrategisches Kalkül, \ die Schwäche der Russen nach Auflösung des Warschauer Paktes auszunutzen, sie mit der NATO zu umzingeln und bei Widerstand dann eben in einem kräftezehrenden Krieg stark zu schwächen und damit ein für alle Male als ökonomische Konkurrenten in Europa auszuschalten scheinbar aufgegangen...\ \ Das paranoide alte und zugleich kindliche „Freund/Feind Schema“ hatte seinen Dienst verrichtet und das „imperiale Böse“ konnte bequem auf „Putin und die Russen“ projiziert werden.
\ Schizophren ist dies auch deswegen, weil mit zweierlei Maß gemessen wurde und wird, denn niemals würden die USA auch nur eine russische Rakete auf Kuba tolerieren und gehen selber - ganz anders als Russland - global weit über die eigene Grenzsicherung hinaus, indem sie sich anmaßen, den gesamten Globus mit fast 800 Militärbasen zu überziehen und je nach Bedarf Kriege zu führen, wenn es ihnen zur Sicherung ihrer Rohstoffe - für auch unseren westlichen Lebensstil - und/oder geostrategischen Macht opportun und machbar erscheint.\ \ Deutschland spielt seit 2022 die naive und mehr als traurige Vorreiterrolle eines unterwürfigen Vasallen der so tut, als würde unsere Freiheit durch gegenseitigen Mord und Totschlag von Hunderttausenden junger Ukrainer und Russen in der Ukraine verteidigt, eine äußerst perverse und dümmliche Vorstellung ohne historische geschweige denn geo-strategische Kenntnisse und Erfahrungswerte.\ \ Demgegenüber ist klar: Es gibt nur EINE Sicherheit in Europa für alle vom Atlantik bis hinter den Ural, oder es gibt KEINE Sicherheit für Niemanden, \ wenn wir nicht die berechtigten Sicherheitsinteressen der Russen ernst nehmen, die wir, d.h. die unsere Väter und Großväter bereits im 20.Jahrhundert rücksichtslos überfallen, mit Krieg überzogen und ermordet haben.\ \ John F. Kennedy und Nikita S. Chruschtschow waren 1962 im historischen Gegenstück zum „Ukrainekrieg“, der „Kubakrise“, weise genug einen Weltkrieg durch gegenseitige Zugeständnisse zu verhindern.
Wo sind die Politiker von Format, die in ihre Fußstapfen treten?\ \ Es wäre eine bitterböse Farce, wenn ausgerechnet ein autoritärer Oligarchen-Präsident wie Donald Trump die Weisheit hätte, diesen Schritt zu tun...\ \ Zugleich wäre die öffentliche Bankrott-Erklärung aller europäischen Politiker, \ die sich als viel demokratischer, sachlicher und menschlicher ansehen \ und ihre eigene dramatische Fehlleistung wohl niemals eingestehen...\ \ Allein die politische wie mediale Empörungswelle in Deutschland, als Trump und Putin ganz offenlegten, wer denn in diesem Krieg das Sagen hat, \ lässt Schlimmstes befürchten. Obwohl aus gut unterrichteten Diplomatenkreisen längst durchgesickert ist, dass im Prinzip die gesamte Analyse hier unter Diplomaten anerkannt und ziemlich nah an den Tatsachen ist, gehört nicht viel Lebenserfahrung dazu zu wissen, dass die meisten der ach so mächtigen westeuropäischen Politiker dies nie zugeben werden...
-
 @ fd06f542:8d6d54cd
2025-03-31 10:00:34
@ fd06f542:8d6d54cd
2025-03-31 10:00:34NIP-05
Mapping Nostr keys to DNS-based internet identifiers
finaloptionalOn events of kind
0(user metadata) one can specify the key"nip05"with an internet identifier (an email-like address) as the value. Although there is a link to a very liberal "internet identifier" specification above, NIP-05 assumes the<local-part>part will be restricted to the charactersa-z0-9-_., case-insensitive.Upon seeing that, the client splits the identifier into
<local-part>and<domain>and use these values to make a GET request tohttps://<domain>/.well-known/nostr.json?name=<local-part>.The result should be a JSON document object with a key
"names"that should then be a mapping of names to hex formatted public keys. If the public key for the given<name>matches thepubkeyfrom theuser metadataevent, the client then concludes that the given pubkey can indeed be referenced by its identifier.Example
If a client sees an event like this:
jsonc { "pubkey": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9", "kind": 0, "content": "{\"name\": \"bob\", \"nip05\": \"bob@example.com\"}" // other fields... }It will make a GET request to
https://example.com/.well-known/nostr.json?name=boband get back a response that will look likejson { "names": { "bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9" } }or with the recommended
"relays"attribute:json { "names": { "bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9" }, "relays": { "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9": [ "wss://relay.example.com", "wss://relay2.example.com" ] } }If the pubkey matches the one given in
"names"(as in the example above) that means the association is right and the"nip05"identifier is valid and can be displayed.The recommended
"relays"attribute may contain an object with public keys as properties and arrays of relay URLs as values. When present, that can be used to help clients learn in which relays the specific user may be found. Web servers which serve/.well-known/nostr.jsonfiles dynamically based on the query string SHOULD also serve the relays data for any name they serve in the same reply when that is available.Finding users from their NIP-05 identifier
A client may implement support for finding users' public keys from internet identifiers, the flow is the same as above, but reversed: first the client fetches the well-known URL and from there it gets the public key of the user, then it tries to fetch the kind
0event for that user and check if it has a matching"nip05".Notes
Identification, not verification
The NIP-05 is not intended to verify a user, but only to identify them, for the purpose of facilitating the exchange of a contact or their search.
Exceptions are people who own (e.g., a company) or are connected (e.g., a project) to a well-known domain, who can exploit NIP-05 as an attestation of their relationship with it, and thus to the organization behind it, thereby gaining an element of trust.User discovery implementation suggestion
A client can use this to allow users to search other profiles. If a client has a search box or something like that, a user may be able to type "bob@example.com" there and the client would recognize that and do the proper queries to obtain a pubkey and suggest that to the user.
Clients must always follow public keys, not NIP-05 addresses
For example, if after finding that
bob@bob.comhas the public keyabc...def, the user clicks a button to follow that profile, the client must keep a primary reference toabc...def, notbob@bob.com. If, for any reason, the addresshttps://bob.com/.well-known/nostr.json?name=bobstarts returning the public key1d2...e3fat any time in the future, the client must not replaceabc...defin his list of followed profiles for the user (but it should stop displaying "bob@bob.com" for that user, as that will have become an invalid"nip05"property).Public keys must be in hex format
Keys must be returned in hex format. Keys in NIP-19
npubformat are only meant to be used for display in client UIs, not in this NIP.Showing just the domain as an identifier
Clients may treat the identifier
_@domainas the "root" identifier, and choose to display it as just the<domain>. For example, if Bob ownsbob.com, he may not want an identifier likebob@bob.comas that is redundant. Instead, Bob can use the identifier_@bob.comand expect Nostr clients to show and treat that as justbob.comfor all purposes.Reasoning for the
/.well-known/nostr.json?name=<local-part>formatBy adding the
<local-part>as a query string instead of as part of the path, the protocol can support both dynamic servers that can generate JSON on-demand and static servers with a JSON file in it that may contain multiple names.Allowing access from JavaScript apps
JavaScript Nostr apps may be restricted by browser CORS policies that prevent them from accessing
/.well-known/nostr.jsonon the user's domain. When CORS prevents JS from loading a resource, the JS program sees it as a network failure identical to the resource not existing, so it is not possible for a pure-JS app to tell the user for certain that the failure was caused by a CORS issue. JS Nostr apps that see network failures requesting/.well-known/nostr.jsonfiles may want to recommend to users that they check the CORS policy of their servers, e.g.:bash $ curl -sI https://example.com/.well-known/nostr.json?name=bob | grep -i ^Access-Control Access-Control-Allow-Origin: *Users should ensure that their
/.well-known/nostr.jsonis served with the HTTP headerAccess-Control-Allow-Origin: *to ensure it can be validated by pure JS apps running in modern browsers.Security Constraints
The
/.well-known/nostr.jsonendpoint MUST NOT return any HTTP redirects.Fetchers MUST ignore any HTTP redirects given by the
/.well-known/nostr.jsonendpoint. -
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Jofer
Jofer era um jogador diferente. À primeira vista não, parecia igual, um volante combativo, perseguia os atacantes adversários implacavelmente, um bom jogador. Mas não era essa a característica que diferenciava Jofer. Jofer era, digamos, um chutador.
Começou numa semifinal de um torneio de juniores. O time de Jofer precisava do empate e estava sofrendo uma baita pressão do adversário, mas o jogo estava 1 a 1 e parecia que ia ficar assim mesmo, daquele jeito futebolístico que parece, parece mesmo. Só que aos 46 do segundo tempo tomaram um gol espírita, Ruizinho do outro time saiu correndo pela esquerda e, mesmo sendo canhoto, foi cortando para o meio, os zagueiros meio que achando que já tinha acabado mesmo, devia ter só mais aquele lance, o árbitro tinha dado dois minutos, Ruizinho chutou, marcou e o goleiro, que só pulou depois que já tinha visto que não ia ter jeito, ficou xingando.
A bola saiu do meio e tocaram para Jofer, ninguém nem veio marcá-lo, o outro time já estava comemorando, e com razão, o juiz estava de sacanagem em fazer o jogo continuar, já estava tudo acabado mesmo. Mas não, estava certo, mais um minuto de acréscimo, justo. Em um minuto dá pra fazer um gol. Mas como? Jofer pensou nas partidas da NBA em que com alguns centésimos de segundo faltando o armador jogava de qualquer jeito para a cesta e às vezes acertava. De trás do meio de campo, será? Não vou ter nem força pra fazer chegar no gol. Vou virar piada, melhor tocar pro Fumaça ali do lado e a gente perde sem essa humilhação no final. Mas, poxa, e daí? Vou tentar mesmo assim, qualquer coisa eu falo que foi um lançamento e daqui a uns dias todo mundo esquece. Olhou para o próprio pé, virou ele de ladinho, pra fora e depois pra dentro (bom, se eu pegar daqui, direitinho, quem sabe?), jogou a bola pro lado e bateu. A bola subiu escandalosamente, muito alta mesmo, deve ter subido uns 200 metros. Jofer não tinha como ter a menor noção. Depois foi descendo, o goleirão voltando correndo para debaixo da trave e olhando pra bola, foi chegando e pulando já só pra acompanhar, para ver, dependurado no travessão, a bola sair ainda bem alta, ela bateu na rede lateral interna antes de bater no chão, quicar violentamente e estufar a rede no alto do lado direito de quem olhava.
Mas isso tudo foi sonho do Jofer. Sonhou acordado, numa noite em que demorou pra dormir, deitado na sua cama. Ficou pensando se não seria fácil, se ele treinasse bastante, acertar o gol bem de longe, tipo no sonho, e se não dava pra fazer gol assim. No dia seguinte perguntou a Brunildinho, o treinador de goleiros. Era difícil defender essas bolas, ainda mais se elas subissem muito, o goleiro ficava sem perspectiva, o vento alterava a trajetória a cada instante, tinha efeito, ela cairia rápido, mas claro que não valia à pena treinar isso, a chance de acertar o gol era minúscula. Mas Jofer só ia tentar depois que treinasse bastante e comprovasse o que na sua imaginação parecia uma excelente idéia.
Começou a treinar todos os dias. Primeiro escondido, por vergonha dos colegas, chegava um pouco antes e ficava lá, chutando do círculo central. Ao menor sinal de gente se aproximando, parava e ia catar as bolas. Depois, quando começou a acertar, perdeu a vergonha. O pessoal do clube todo achava engraçado quando via Jofer treinando e depois ouvia a explicação da boca de alguém, ninguém levava muito a sério, mas também não achava de todo ridículo. O pessoal ria, mas no fundo torcia praquilo dar certo, mesmo.
Aconteceu que num jogo que não valia muita coisa, empatezinho feio, aos 40 do segundo tempo, a marcação dos adversários já não estava mais pressionando, todo mundo contente com o empate e com vontade de parar de jogar já, o Henrique, meia-esquerdo, humilde, mas ainda assim um pouco intimidante para Jofer (jogava demais), tocou pra ele. Vai lá, tenta sua loucura aí. Assumiu a responsabilidade do nosso volante introspectivo. Seria mais verossímil se Jofer tivesse errado, primeira vez que tentou, restava muito tempo ainda pra ele ter a chance de ser herói, ninguém acerta de primeira, mas ele acertou. Quase como no sonho, Lucas, o goleiro, não esperava, depois que viu o lance, riu-se, adiantou-se para pegar a bola que ele julgava que quicaria na área, mas ela foi mais pra frente, mais e mais, daí Lucas já estava correndo, só que começou a pensar que ela ia pra fora, e ele ia só se dependurar no travessão e fazer seu papel de estar na bola. Acabou que por conta daquele gol eles terminaram em segundo no grupo daquele torneiozinho, ao invés de terceiro, e não fez diferença nenhuma.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28The flaw of "just use paypal/coinbase" arguments
For the millionth time I read somewhere that "custodial bitcoin is not bitcoin" and that "if you're going to use custodial, better use Paypal". No, actually it was "better use Coinbase", but I had heard the "PayPal" version in the past.
There are many reasons why using PayPal is not the same as using a custodial Bitcoin service or wallet that are obvious and not relevant here, such as the fact that you can't have Bitcoin balances on Bitcoin (or maybe now you can? but you can't send it around); plus all the reasons that are also valid for Coinbase such as you having to give all your data and selfies of yourself and your government documents and so on -- but let's ignore these reasons for now.
The most important reason why it isn't the same thing is that when you're using Coinbase you are stuck in Coinbase. Your Coinbase coins cannot be used to pay anyone that isn't in Coinbase. So Coinbase-style custodianship doesn't help Bitcoin. If you want to move out of Coinbase you have to withdraw from Coinbase.
Custodianship on Lightning is of a very different nature. You can pay people from other custodial platforms and people that are hosting their own Lightning nodes and so on.
That kind of custodianship doesn't do any harm to anyone, doesn't fracture the network, doesn't reduce the network effect of Lightning, in fact it increases it.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28My personal experience (as a complete ignorant) of the blocksize debate in 2017
In the beginning of 2017 I didn't know Bitcoin was having a "blocksize debate". I had stopped paying attention to Bitcoin in 2014 after reading Tim Swanson's book on shitcoineiry and was surprise people even care about Bitcoin still while Ethereum and other fancy things were around.
My introduction to the subject was this interview with Andrew Stone and Andrew Clifford from Bitcoin Unlimited (still don't know who these guys are). I've listened to it and kinda liked the conspiracy theory about "a group of developers trying, against miners and users, to control the whole ecosystem by not allowing blocks to grow" (actually, if you listen to this interview that announced the creation of Blockstream and the sidechains whitepaper it does sound like a government agent bribing all the Core developers into forming a consortium that will turn Bitcoin into an Ethereum-like shitcoin under their control -- but this is just a useless digression).
Some time later I listened to this interview with Jimmy Song and was introduced to two hard forks and conspiracies and New York Agreement and got excited because I didn't care about Bitcoin (I'm ashamed to remember this feeling) and wanted to see things changing, people fighting, Bitcoin burning, for no reason. Oddly, what I grasped from the interview was that Jimmy Song was defending the agreement and expecting everybody to fulfill it.
When the day actually come and "Bitcoin Cash" forked I looked at it with pity because it looked clearly a failure from the beginning, but I still cheered for it a bit, still not knowing anything about the debate, besides the fact that blocks were bigger on BCH, which looked like a very reductionist explanation to me.
"Of course it's not just making blocks bigger, that would be too simple, they probably have a very complex plan I'm not apt to understand", I thought.
To my surprise the entire argument was actually just that: bigger blocks bigger blocks. I came to that conclusion by listening to tomwoods.com/1064, a debate in which reasonable arguments faced childish claims. That debate gave me perspective and was a clear, undisputed win from Jameson Lopp against Roger Ver.
Actually some time before that I had listened to another Tom Woods Show episode thinking it was going to be an episode about Bitcoin, but in fact it was just propaganda about a debate I had almost forgotten. And nothing about Bitcoin, everything about "Bitcoin Cash" and how there were two Bitcoins, one legitimate and the other unlegitimate.
So, from the perspective of someone that came to the debate totally fresh and only listens to the big-blocker arguments for a long time, they still don't convince anyone with some common sense (as I would like to think of myself), they just sound like mad dogs and everything goes against themselves.
Fast forward to the present and with much more understanding of the issues in place I started digging some material from 2016-2017 about the debate to try to get more context, and found this ridiculous interview with Mike Hearn. It isn't a waste of time to listen to it if you're not familiar with the debate from that time.
As I should have probably expected from my experience with Epicenter.tv, both the interviewers agree with Mike Hearn about his ridiculous claims about how (not his words) we have to subsidize the few thousand current Bitcoin users by preventing fees from increase and there are no trade-offs to doing that -- and even with everybody agreeing they all manage to sound stupid. There's not a single phrase that is defendable in the entire interview, no criticisms make any sense, it makes me feel bad for the the guy as he feels so self-assured and obviouslyright.
After knowing about these and other adventures of stupid people with high influences in the Bitcoin world trying to impose their idiocy on others it feels even more odd and unexpected to find Bitcoin in the right track. Generally in politics the most dumb wins, but apparently not in Bitcoin.
Bitcoin is a miracle.
-
 @ 7d33ba57:1b82db35
2025-03-31 09:28:36
@ 7d33ba57:1b82db35
2025-03-31 09:28:36Rovinj is one of Croatia’s most beautiful coastal towns, known for its colorful Venetian-style buildings, cobblestone streets, and breathtaking sea views. Located on the Istrian Peninsula, Rovinj offers a mix of history, culture, and stunning beaches, making it a perfect getaway for travelers seeking both relaxation and adventure.
🌊 Top Things to See & Do in Rovinj
1️⃣ Explore Rovinj Old Town 🏡
- Wander through narrow, winding streets filled with art galleries, boutique shops, and charming cafés.
- Discover Balbi’s Arch, the old entrance to the city, and the Clock Tower.
- Enjoy stunning sunset views from the harbor.
2️⃣ Visit St. Euphemia’s Church ⛪
- The most famous landmark in Rovinj, located at the highest point of the Old Town.
- Climb the bell tower for a panoramic view of the Adriatic and nearby islands.
- Learn about Saint Euphemia, the town’s patron saint, and her fascinating legend.
3️⃣ Relax at Rovinj’s Best Beaches 🏖️
- Lone Bay Beach – A popular spot near Zlatni Rt forest, great for swimming.
- Mulini Beach – A stylish beach with a cocktail bar and clear waters.
- Cuvi Beach – A quieter, family-friendly pebble beach.
4️⃣ Walk or Cycle Through Golden Cape Forest Park (Zlatni Rt) 🌿🚲
- A protected nature park with pine forests, walking trails, and hidden coves.
- Great for hiking, cycling, and rock climbing.
- Perfect for a picnic with sea views.
5️⃣ Take a Boat Trip to Rovinj Archipelago 🛥️
- Explore Red Island (Crveni Otok) – A peaceful getaway with sandy beaches.
- Visit St. Andrew’s Island, home to a former Benedictine monastery.
- Sunset dolphin-watching tours are a must! 🐬
6️⃣ Try Authentic Istrian Cuisine 🍽️
- Fuži with truffles – A local pasta dish with Istria’s famous truffles.
- Istrian seafood platter – Fresh fish, mussels, and Adriatic shrimp.
- Olive oil & wine tasting – Try local Malvazija (white) and Teran (red) wines.
7️⃣ Visit the Batana House Museum ⛵
- A unique museum dedicated to Rovinj’s traditional wooden fishing boats (batanas).
- Learn about local fishing traditions and maritime culture.
- End the visit with a traditional batana boat ride at sunset.
🚗 How to Get to Rovinj
✈️ By Air: The nearest airport is Pula Airport (PUY), 40 km away.
🚘 By Car:
- From Pula: ~40 min (40 km)
- From Zagreb: ~3 hours (250 km)
- From Ljubljana (Slovenia): ~2.5 hours (170 km)
🚌 By Bus: Direct buses from Pula, Rijeka, and Zagreb.
🚢 By Ferry: Seasonal ferries connect Rovinj with Venice, Italy (~2.5 hours).💡 Tips for Visiting Rovinj
✅ Best time to visit? May–September for warm weather & festivals ☀️
✅ Wear comfy shoes – The Old Town streets are made of polished stone & can be slippery 👟
✅ Book restaurants in advance – Rovinj is a foodie hotspot, especially in summer 🍷
✅ Take a sunset walk along the harbor – One of the most romantic views in Croatia 🌅
✅ Bring cash – Some smaller shops and taverns still prefer cash 💶 -
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28idea: Per-paragraph paywalls
Using the lnurl-allowance protocol, a website could instead of putting a paywall over the entire site, charge a reader for only the paragraphs they read. Of course this requires trust from the reader on the website, but this is normal. The website could just hide the rest of the article before an invoice from the paragraph just read was paid.
This idea came from Colin from the Unhashed Podcast.
Could also work with podcasts and videos.
-
 @ 5fb7f8f7:d7d76024
2025-03-31 09:14:45
@ 5fb7f8f7:d7d76024
2025-03-31 09:14:45Imagine a world where your voice is truly yours where no algorithm buries your posts, no central authority censors your ideas, and no account bans silence you. Welcome to yakiHonne, the decentralized media revolution built on Nostr.
Here, freedom reigns. Whether you're sharing breaking news, deep thoughts, or creative content, yakiHonne ensures your voice is unstoppable. No corporate overlords, no gatekeepers, just pure, open communication between people who value truth and transparency.
Why yakiHonne?
✅ Censorship-Free: Speak your mind without fear of bans or shadowbans. ✅ Decentralized & Secure: Your content lives on the blockchain, not in the hands of a single company. ✅ Community-Driven: Connect with like-minded individuals who believe in free expression. ✅ Future-Proof: No central server means no risk of takedowns or content wipes.
Break away from the limits of traditional media. Join yakiHonne today and take control of your voice!
-
 @ 78c90fc4:4bff983c
2025-03-31 08:13:17
@ 78c90fc4:4bff983c
2025-03-31 08:13:17Die Operation „Cast Thy Bread“ war eine verdeckte Kampagne zur biologischen Kriegsführung, die von der Haganah und später von den israelischen Verteidigungsstreitkräften während des arabisch-israelischen Krieges 1948 durchgeführt wurde[1][3]. Bei der Operation, die im April 1948 begann, wurden Trinkwasserquellen mit Typhusbakterien verseucht, um palästinensisch-arabische Zivilisten und verbündete arabische Armeen anzugreifen[1][3].
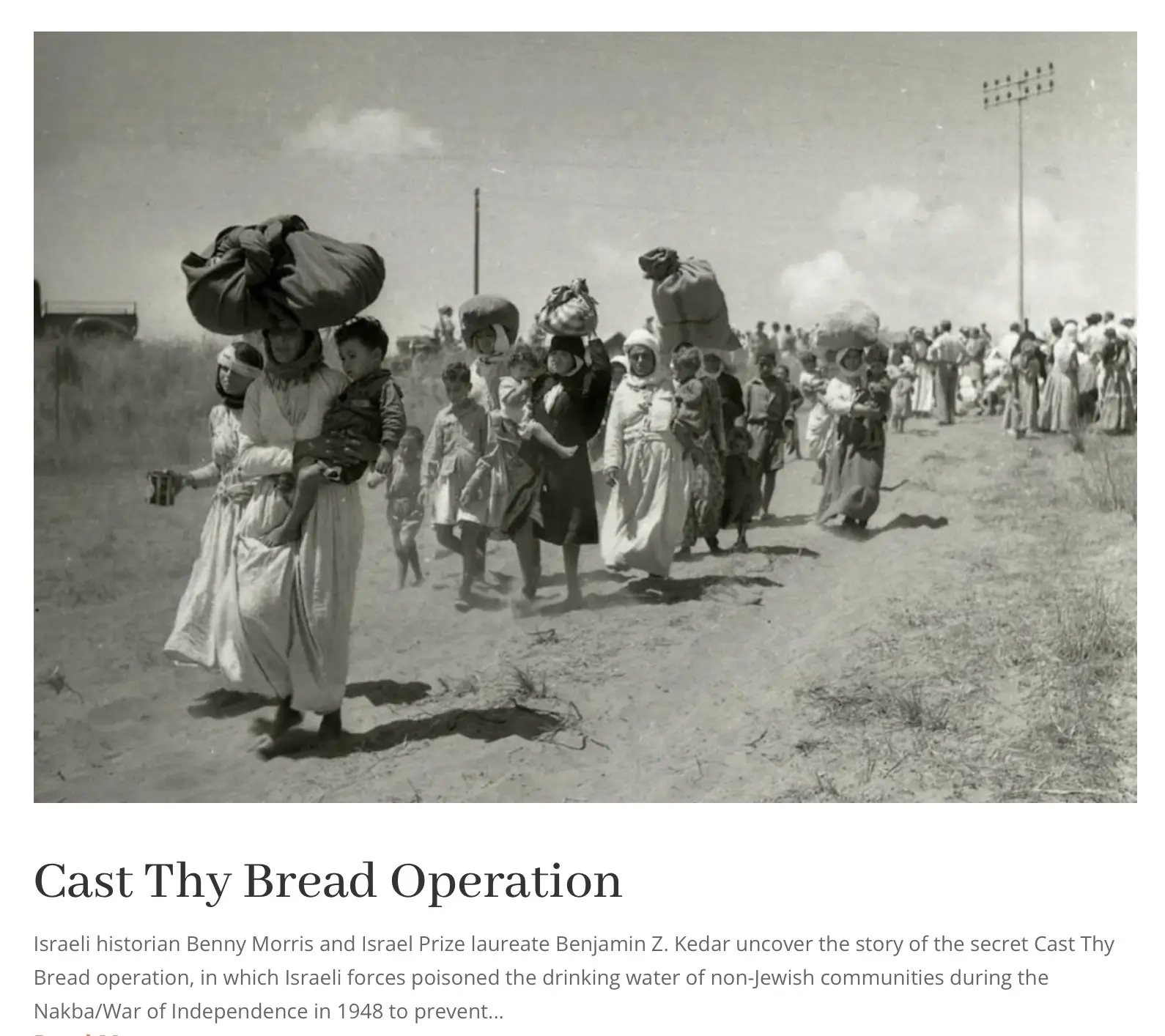
\ \ ## Wichtige Details\ \ - **Ziel**: Palästinensische Araber an der Rückkehr in eroberte Dörfer zu hindern und die Versuche der arabischen Armeen, Gebiete zurückzuerobern, zu behindern[1].\ - **Methoden**: Israelische Streitkräfte setzten Typhuskeime in Flaschen, Reagenzgläsern und Thermoskannen ein, um Brunnen und Wasservorräte in palästinensischen Gebieten zu vergiften[1][3].\ - **Führung**: Die Operation wurde vom israelischen Premierminister David Ben-Gurion und dem Generalstabschef der IDF, Yigael Yadin, beaufsichtigt und genehmigt[1].\ \ ## Bemerkenswerte Vorfälle\ \ - Akkon (Akka)**: Die Wasserversorgung der Stadt wurde am 15. Mai 1948 verseucht, was zu einer Typhusepidemie und „extremer Verzweiflung“ unter den Einwohnern führte[1][3].\ - **Gaza**: Im Mai 1948 versuchten vier Soldaten der israelischen Spezialeinheiten, die örtliche Wasserversorgung zu vergiften, wurden jedoch gefangen genommen und hingerichtet[1].\ - **Andere Orte**: Auch in Jericho, Eilabun und palästinensischen Vierteln in Jerusalem wurden Brunnen vergiftet[1][3].\ \ ## Folgen\ \ Die Operation führte zu schweren Erkrankungen unter den palästinensischen Anwohnern, von denen Dutzende betroffen sein sollen[1][3]. Sie erzielte jedoch nicht die von ihren Befürwortern erhoffte lähmende Wirkung und wurde im Dezember 1948 eingestellt[1].\ \ ## Historische Bedeutung\ \ Die Operation „Gegossenes Brot“ wurde als Kriegsverbrechen und als Akt der ethnischen Säuberung eingestuft[1]. Ihre Enthüllung hat eine Kontroverse und Debatte über die im Krieg von 1948 angewandten Taktiken und ihre langfristigen Auswirkungen auf den israelisch-palästinensischen Konflikt ausgelöst[2][4].
Quellen
[1] Operation Cast Thy Bread - Wikipedia https\://en.wikipedia.org/wiki/Operation_Cast_Thy_Bread
[2] Cast Thy Bread Archives - Promised Land Museum https\://promisedlandmuseum.org/tag/cast-thy-bread/
[3] From 'Virtuous Boy' to Murderous Fanatic: David Ben-Gurion and the ... https\://www.euppublishing.com/doi/10.3366/hlps.2023.0308
[4] Historians reveal Israel's use of poison against Palestinians https\://www.middleeastmonitor.com/20221011-historians-reveal-israels-use-of-poison-against-palestinians/
[5] Thoughts on Operation Cast Thy Bread? : r/IsraelPalestine - Reddit https\://www.reddit.com/r/IsraelPalestine/comments/1g02b64/thoughts_on_operation_cast_thy_bread/
[6] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www.tandfonline.com/doi/abs/10.1080/00263206.2022.2122448
[7] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://cris.bgu.ac.il/en/publications/cast-thy-bread-israeli-biological-warfare-during-the-1948-war
[8] 'Cast thy bread': Israeli biological warfare during the 1948 War https\://www.tandfonline.com/doi/full/10.1080/00263206.2022.2122448
\
Artikel https://x.com/RealWsiegrist/status/1906616394747179136
Nakba
https://waltisiegrist.locals.com/upost/2033124/die-siedler-fordern-ganz-offen-eine-zweite-nakba
-
 @ 22aa8151:ae9b5954
2025-03-31 07:44:15
@ 22aa8151:ae9b5954
2025-03-31 07:44:15With all the current hype around Payjoin for the month, I'm open-sourcing a project I developed five years ago: https://github.com/Kukks/PrivatePond
Note: this project is unmaintained and should only be used as inspiration.
Private Pond is a Bitcoin Payjoin application I built specifically to optimize Bitcoin transaction rails for services, such as deposits, withdrawals, and automated wallet rebalancing.
The core concept is straightforward: withdrawals requested by users are queued and processed at fixed intervals, enabling traditional, efficient transaction batching. Simultaneously, deposits from other users can automatically batch these withdrawals via Payjoin batching, reducing them onchain footprint further. Taking it to the next step: a user's deposit is able to fund the withdrawals with its own funds reducing the required operational liquidity in hot wallets through a process called the Meta Payjoin.
The application supports multiple wallets—hot, cold, multisig, or hybrid—with configurable rules, enabling automated internal fund management and seamless rebalancing based on operational needs such as min/max balance limits and wallet ratios (10% hot, 80% in 2-of-3, 10% in 1-of-2, etc) .
This system naturally leverages user Payjoin transactions as part of the automated rebalancing strategy, improving liquidity management by batching server operations with user interactions.
Private Pond remains quite possibly the most advanced Payjoin project today, though my multi-party addendum of 2023 probably competes. That said, Payjoin adoption overall has been disappointing: the incentives heavily favor service operators who must in turn actively encourage user participation, limiting its appeal only for specialized usage. This is why my efforts refocused on systems like Wabisabi coinjoins, delivering not just great privacy but all the benefits of advanced Payjoin batching on a greater scale through output compaction.
Soon, I'll also open-source my prototype coinjoin protocol, Kompaktor, demonstrating significant scalability improvements, such as 50+ payments from different senders being compacted into a single Bitcoin output. And this is not even mentioning Ark, that pushes these concepts even further, giving insane scalability and asyncrhonous execution.
You can take a look at the slides I did around this here: https://miro.com/app/board/uXjVL-UqP4g=/
Parts of Private Pond, the pending transfers and multisig, will soon be integrated into nostr:npub155m2k8ml8sqn8w4dhh689vdv0t2twa8dgvkpnzfggxf4wfughjsq2cdcvg 's next major release—special thanks to nostr:npub1j8y6tcdfw3q3f3h794s6un0gyc5742s0k5h5s2yqj0r70cpklqeqjavrvg for continuing the work and getting it to the finish line.
-
 @ 4ba8e86d:89d32de4
2025-04-28 22:39:20
@ 4ba8e86d:89d32de4
2025-04-28 22:39:20Como funciona o PGP.
O texto a seguir foi retirado do capítulo 1 do documento Introdução à criptografia na documentação do PGP 6.5.1. Copyright © 1990-1999 Network Associates, Inc. Todos os direitos reservados.
-O que é criptografia? -Criptografia forte -Como funciona a criptografia? -Criptografia convencional -Cifra de César -Gerenciamento de chaves e criptografia convencional -Criptografia de chave pública -Como funciona o PGP - Chaves • Assinaturas digitais -Funções hash • Certificados digitais -Distribuição de certificados -Formatos de certificado •Validade e confiança -Verificando validade -Estabelecendo confiança -Modelos de confiança • Revogação de certificado -Comunicar que um certificado foi revogado -O que é uma senha? -Divisão de chave
Os princípios básicos da criptografia.
Quando Júlio César enviou mensagens aos seus generais, ele não confiou nos seus mensageiros. Então ele substituiu cada A em suas mensagens por um D, cada B por um E, e assim por diante através do alfabeto. Somente alguém que conhecesse a regra “shift by 3” poderia decifrar suas mensagens. E assim começamos.
Criptografia e descriptografia.
Os dados que podem ser lidos e compreendidos sem quaisquer medidas especiais são chamados de texto simples ou texto não criptografado. O método de disfarçar o texto simples de forma a ocultar sua substância é chamado de criptografia. Criptografar texto simples resulta em um jargão ilegível chamado texto cifrado. Você usa criptografia para garantir que as informações sejam ocultadas de qualquer pessoa a quem não se destinam, mesmo daqueles que podem ver os dados criptografados. O processo de reverter o texto cifrado ao texto simples original é chamado de descriptografia . A Figura 1-1 ilustra esse processo.
https://image.nostr.build/0e2fcb71ed86a6083e083abbb683f8c103f44a6c6db1aeb2df10ae51ec97ebe5.jpg
Figura 1-1. Criptografia e descriptografia
O que é criptografia?
Criptografia é a ciência que usa a matemática para criptografar e descriptografar dados. A criptografia permite armazenar informações confidenciais ou transmiti-las através de redes inseguras (como a Internet) para que não possam ser lidas por ninguém, exceto pelo destinatário pretendido. Embora a criptografia seja a ciência que protege os dados, a criptoanálise é a ciência que analisa e quebra a comunicação segura. A criptoanálise clássica envolve uma combinação interessante de raciocínio analítico, aplicação de ferramentas matemáticas, descoberta de padrões, paciência, determinação e sorte. Os criptoanalistas também são chamados de atacantes. A criptologia abrange tanto a criptografia quanto a criptoanálise.
Criptografia forte.
"Existem dois tipos de criptografia neste mundo: a criptografia que impedirá a sua irmã mais nova de ler os seus arquivos, e a criptografia que impedirá os principais governos de lerem os seus arquivos. Este livro é sobre o último." --Bruce Schneier, Criptografia Aplicada: Protocolos, Algoritmos e Código Fonte em C. PGP também trata deste último tipo de criptografia. A criptografia pode ser forte ou fraca, conforme explicado acima. A força criptográfica é medida no tempo e nos recursos necessários para recuperar o texto simples. O resultado de uma criptografia forte é um texto cifrado que é muito difícil de decifrar sem a posse da ferramenta de decodificação apropriada. Quão díficil? Dado todo o poder computacional e o tempo disponível de hoje – mesmo um bilhão de computadores fazendo um bilhão de verificações por segundo – não é possível decifrar o resultado de uma criptografia forte antes do fim do universo. Alguém poderia pensar, então, que uma criptografia forte resistiria muito bem até mesmo contra um criptoanalista extremamente determinado. Quem pode realmente dizer? Ninguém provou que a criptografia mais forte disponível hoje resistirá ao poder computacional de amanhã. No entanto, a criptografia forte empregada pelo PGP é a melhor disponível atualmente.
Contudo, a vigilância e o conservadorismo irão protegê-lo melhor do que as alegações de impenetrabilidade.
Como funciona a criptografia?
Um algoritmo criptográfico, ou cifra, é uma função matemática usada no processo de criptografia e descriptografia. Um algoritmo criptográfico funciona em combinação com uma chave – uma palavra, número ou frase – para criptografar o texto simples. O mesmo texto simples é criptografado em texto cifrado diferente com chaves diferentes. A segurança dos dados criptografados depende inteiramente de duas coisas: a força do algoritmo criptográfico e o sigilo da chave. Um algoritmo criptográfico, mais todas as chaves possíveis e todos os protocolos que o fazem funcionar constituem um criptossistema. PGP é um criptossistema.
Criptografia convencional.
Na criptografia convencional, também chamada de criptografia de chave secreta ou de chave simétrica , uma chave é usada tanto para criptografia quanto para descriptografia. O Data Encryption Standard (DES) é um exemplo de criptossistema convencional amplamente empregado pelo Governo Federal. A Figura 1-2 é uma ilustração do processo de criptografia convencional. https://image.nostr.build/328b73ebaff84c949df2560bbbcec4bc3b5e3a5163d5fbb2ec7c7c60488f894c.jpg
Figura 1-2. Criptografia convencional
Cifra de César.
Um exemplo extremamente simples de criptografia convencional é uma cifra de substituição. Uma cifra de substituição substitui uma informação por outra. Isso é feito com mais frequência compensando as letras do alfabeto. Dois exemplos são o Anel Decodificador Secreto do Capitão Meia-Noite, que você pode ter possuído quando era criança, e a cifra de Júlio César. Em ambos os casos, o algoritmo serve para compensar o alfabeto e a chave é o número de caracteres para compensá-lo. Por exemplo, se codificarmos a palavra "SEGREDO" usando o valor chave de César de 3, deslocaremos o alfabeto para que a terceira letra abaixo (D) comece o alfabeto. Então começando com A B C D E F G H I J K L M N O P Q R S T U V W X Y Z e deslizando tudo para cima em 3, você obtém DEFGHIJKLMNOPQRSTUVWXYZABC onde D=A, E=B, F=C e assim por diante. Usando este esquema, o texto simples, "SECRET" é criptografado como "VHFUHW". Para permitir que outra pessoa leia o texto cifrado, você diz a ela que a chave é 3. Obviamente, esta é uma criptografia extremamente fraca para os padrões atuais, mas, ei, funcionou para César e ilustra como funciona a criptografia convencional.
Gerenciamento de chaves e criptografia convencional.
A criptografia convencional tem benefícios. É muito rápido. É especialmente útil para criptografar dados que não vão a lugar nenhum. No entanto, a criptografia convencional por si só como meio de transmissão segura de dados pode ser bastante cara, simplesmente devido à dificuldade de distribuição segura de chaves. Lembre-se de um personagem do seu filme de espionagem favorito: a pessoa com uma pasta trancada e algemada ao pulso. Afinal, o que há na pasta? Provavelmente não é o código de lançamento de mísseis/fórmula de biotoxina/plano de invasão em si. É a chave que irá descriptografar os dados secretos. Para que um remetente e um destinatário se comuniquem com segurança usando criptografia convencional, eles devem chegar a um acordo sobre uma chave e mantê-la secreta entre si. Se estiverem em locais físicos diferentes, devem confiar em um mensageiro, no Bat Phone ou em algum outro meio de comunicação seguro para evitar a divulgação da chave secreta durante a transmissão. Qualquer pessoa que ouvir ou interceptar a chave em trânsito poderá posteriormente ler, modificar e falsificar todas as informações criptografadas ou autenticadas com essa chave. Do DES ao Anel Decodificador Secreto do Capitão Midnight, o problema persistente com a criptografia convencional é a distribuição de chaves: como você leva a chave ao destinatário sem que alguém a intercepte?
Criptografia de chave pública.
Os problemas de distribuição de chaves são resolvidos pela criptografia de chave pública, cujo conceito foi introduzido por Whitfield Diffie e Martin Hellman em 1975. (Há agora evidências de que o Serviço Secreto Britânico a inventou alguns anos antes de Diffie e Hellman, mas a manteve um segredo militar - e não fez nada com isso.
[JH Ellis: The Possibility of Secure Non-Secret Digital Encryption, CESG Report, January 1970]) A criptografia de chave pública é um esquema assimétrico que usa um par de chaves para criptografia: uma chave pública, que criptografa os dados, e uma chave privada ou secreta correspondente para descriptografia. Você publica sua chave pública para o mundo enquanto mantém sua chave privada em segredo. Qualquer pessoa com uma cópia da sua chave pública pode criptografar informações que somente você pode ler. Até mesmo pessoas que você nunca conheceu. É computacionalmente inviável deduzir a chave privada da chave pública. Qualquer pessoa que possua uma chave pública pode criptografar informações, mas não pode descriptografá-las. Somente a pessoa que possui a chave privada correspondente pode descriptografar as informações. https://image.nostr.build/fdb71ae7a4450a523456827bdd509b31f0250f63152cc6f4ba78df290887318b.jpg
Figura 1-3. Criptografia de chave pública O principal benefício da criptografia de chave pública é que ela permite que pessoas que não possuem nenhum acordo de segurança pré-existente troquem mensagens com segurança. A necessidade de remetente e destinatário compartilharem chaves secretas através de algum canal seguro é eliminada; todas as comunicações envolvem apenas chaves públicas e nenhuma chave privada é transmitida ou compartilhada. Alguns exemplos de criptossistemas de chave pública são Elgamal (nomeado em homenagem a seu inventor, Taher Elgamal), RSA (nomeado em homenagem a seus inventores, Ron Rivest, Adi Shamir e Leonard Adleman), Diffie-Hellman (nomeado, você adivinhou, em homenagem a seus inventores). ) e DSA, o algoritmo de assinatura digital (inventado por David Kravitz). Como a criptografia convencional já foi o único meio disponível para transmitir informações secretas, o custo dos canais seguros e da distribuição de chaves relegou a sua utilização apenas àqueles que podiam pagar, como governos e grandes bancos (ou crianças pequenas com anéis descodificadores secretos). A criptografia de chave pública é a revolução tecnológica que fornece criptografia forte para as massas adultas. Lembra do mensageiro com a pasta trancada e algemada ao pulso? A criptografia de chave pública o tira do mercado (provavelmente para seu alívio).
Como funciona o PGP.
O PGP combina alguns dos melhores recursos da criptografia convencional e de chave pública. PGP é um criptossistema híbrido. Quando um usuário criptografa texto simples com PGP, o PGP primeiro compacta o texto simples. A compactação de dados economiza tempo de transmissão do modem e espaço em disco e, mais importante ainda, fortalece a segurança criptográfica. A maioria das técnicas de criptoanálise explora padrões encontrados no texto simples para quebrar a cifra. A compressão reduz esses padrões no texto simples, aumentando assim enormemente a resistência à criptoanálise. (Arquivos que são muito curtos para compactar ou que não são compactados bem não são compactados.) O PGP então cria uma chave de sessão, que é uma chave secreta única. Esta chave é um número aleatório gerado a partir dos movimentos aleatórios do mouse e das teclas digitadas. Esta chave de sessão funciona com um algoritmo de criptografia convencional rápido e muito seguro para criptografar o texto simples; o resultado é texto cifrado. Depois que os dados são criptografados, a chave da sessão é criptografada na chave pública do destinatário. Essa chave de sessão criptografada com chave pública é transmitida junto com o texto cifrado ao destinatário.
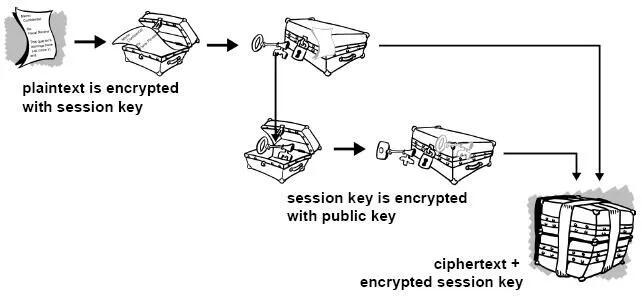
Figura 1-4. Como funciona a criptografia PGP A descriptografia funciona ao contrário. A cópia do PGP do destinatário usa sua chave privada para recuperar a chave de sessão temporária, que o PGP usa para descriptografar o texto cifrado criptografado convencionalmente.

Figura 1-5. Como funciona a descriptografia PGP A combinação dos dois métodos de criptografia combina a conveniência da criptografia de chave pública com a velocidade da criptografia convencional. A criptografia convencional é cerca de 1.000 vezes mais rápida que a criptografia de chave pública. A criptografia de chave pública, por sua vez, fornece uma solução para
problemas de distribuição de chaves e transmissão de dados. Usados em conjunto, o desempenho e a distribuição de chaves são melhorados sem qualquer sacrifício na segurança.
Chaves.
Uma chave é um valor que funciona com um algoritmo criptográfico para produzir um texto cifrado específico. As chaves são basicamente números muito, muito, muito grandes. O tamanho da chave é medido em bits; o número que representa uma chave de 1024 bits é enorme. Na criptografia de chave pública, quanto maior a chave, mais seguro é o texto cifrado. No entanto, o tamanho da chave pública e o tamanho da chave secreta da criptografia convencional não têm nenhuma relação. Uma chave convencional de 80 bits tem a força equivalente a uma chave pública de 1.024 bits. Uma chave convencional de 128 bits é equivalente a uma chave pública de 3.000 bits. Novamente, quanto maior a chave, mais segura, mas os algoritmos usados para cada tipo de criptografia são muito diferentes e, portanto, a comparação é como a de maçãs com laranjas. Embora as chaves pública e privada estejam matematicamente relacionadas, é muito difícil derivar a chave privada dada apenas a chave pública; no entanto, derivar a chave privada é sempre possível, desde que haja tempo e capacidade computacional suficientes. Isto torna muito importante escolher chaves do tamanho certo; grande o suficiente para ser seguro, mas pequeno o suficiente para ser aplicado rapidamente. Além disso, você precisa considerar quem pode estar tentando ler seus arquivos, quão determinados eles estão, quanto tempo têm e quais podem ser seus recursos. Chaves maiores serão criptograficamente seguras por um longo período de tempo. Se o que você deseja criptografar precisar ficar oculto por muitos anos, você pode usar uma chave muito grande. Claro, quem sabe quanto tempo levará para determinar sua chave usando os computadores mais rápidos e eficientes de amanhã? Houve um tempo em que uma chave simétrica de 56 bits era considerada extremamente segura. As chaves são armazenadas de forma criptografada. O PGP armazena as chaves em dois arquivos no seu disco rígido; um para chaves públicas e outro para chaves privadas. Esses arquivos são chamados de chaveiros. Ao usar o PGP, você normalmente adicionará as chaves públicas dos seus destinatários ao seu chaveiro público. Suas chaves privadas são armazenadas em seu chaveiro privado. Se você perder seu chaveiro privado, não será possível descriptografar nenhuma informação criptografada nas chaves desse anel.
Assinaturas digitais.
Um grande benefício da criptografia de chave pública é que ela fornece um método para empregar assinaturas digitais. As assinaturas digitais permitem ao destinatário da informação verificar a autenticidade da origem da informação e também verificar se a informação está intacta. Assim, as assinaturas digitais de chave pública fornecem autenticação e integridade de dados. A assinatura digital também proporciona o não repúdio, o que significa que evita que o remetente alegue que não enviou realmente as informações. Esses recursos são tão fundamentais para a criptografia quanto a privacidade, se não mais. Uma assinatura digital tem a mesma finalidade de uma assinatura manuscrita. No entanto, uma assinatura manuscrita é fácil de falsificar. Uma assinatura digital é superior a uma assinatura manuscrita porque é quase impossível de ser falsificada, além de atestar o conteúdo da informação, bem como a identidade do signatário.
Algumas pessoas tendem a usar mais assinaturas do que criptografia. Por exemplo, você pode não se importar se alguém souber que você acabou de depositar US$ 1.000 em sua conta, mas quer ter certeza de que foi o caixa do banco com quem você estava lidando. A maneira básica pela qual as assinaturas digitais são criadas é ilustrada na Figura 1-6 . Em vez de criptografar informações usando a chave pública de outra pessoa, você as criptografa com sua chave privada. Se as informações puderem ser descriptografadas com sua chave pública, elas deverão ter se originado em você.
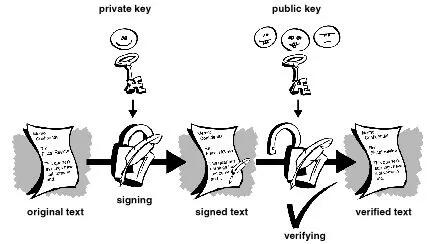
Figura 1-6. Assinaturas digitais simples
Funções hash.
O sistema descrito acima apresenta alguns problemas. É lento e produz um enorme volume de dados – pelo menos o dobro do tamanho da informação original. Uma melhoria no esquema acima é a adição de uma função hash unidirecional no processo. Uma função hash unidirecional recebe uma entrada de comprimento variável – neste caso, uma mensagem de qualquer comprimento, até mesmo milhares ou milhões de bits – e produz uma saída de comprimento fixo; digamos, 160 bits. A função hash garante que, se a informação for alterada de alguma forma – mesmo que por apenas um bit – seja produzido um valor de saída totalmente diferente. O PGP usa uma função hash criptograficamente forte no texto simples que o usuário está assinando. Isso gera um item de dados de comprimento fixo conhecido como resumo da mensagem. (Novamente, qualquer alteração nas informações resulta em um resumo totalmente diferente.) Então o PGP usa o resumo e a chave privada para criar a “assinatura”. O PGP transmite a assinatura e o texto simples juntos. Ao receber a mensagem, o destinatário utiliza o PGP para recalcular o resumo, verificando assim a assinatura. O PGP pode criptografar o texto simples ou não; assinar texto simples é útil se alguns dos destinatários não estiverem interessados ou não forem capazes de verificar a assinatura. Desde que uma função hash segura seja usada, não há como retirar a assinatura de alguém de um documento e anexá-la a outro, ou alterar uma mensagem assinada de qualquer forma. A menor alteração em um documento assinado causará falha no processo de verificação da assinatura digital.
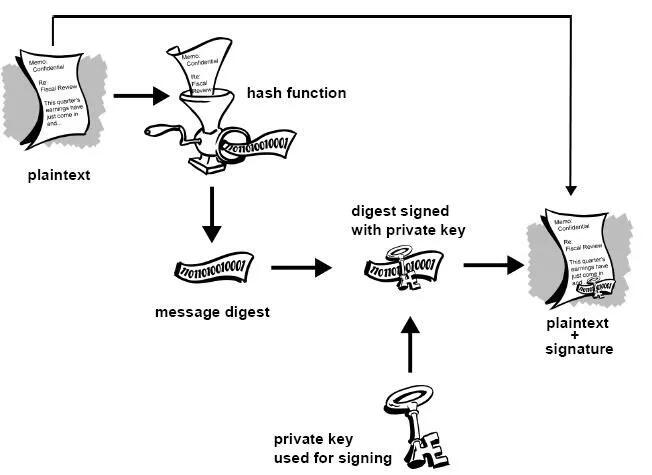
Figura 1-7. Assinaturas digitais seguras As assinaturas digitais desempenham um papel importante na autenticação e validação de chaves de outros usuários PGP.
Certificados digitais.
Um problema com os criptosistemas de chave pública é que os usuários devem estar constantemente vigilantes para garantir que estão criptografando com a chave da pessoa correta. Num ambiente onde é seguro trocar chaves livremente através de servidores públicos, os ataques man-in-the-middle são uma ameaça potencial. Neste tipo de ataque, alguém publica uma chave falsa com o nome e ID de usuário do destinatário pretendido. Os dados criptografados – e interceptados por – o verdadeiro proprietário desta chave falsa estão agora em mãos erradas. Em um ambiente de chave pública, é vital que você tenha certeza de que a chave pública para a qual você está criptografando os dados é de fato a chave pública do destinatário pretendido e não uma falsificação. Você pode simplesmente criptografar apenas as chaves que foram entregues fisicamente a você. Mas suponha que você precise trocar informações com pessoas que nunca conheceu; como você pode saber se tem a chave correta? Os certificados digitais, ou certs, simplificam a tarefa de estabelecer se uma chave pública realmente pertence ao suposto proprietário. Um certificado é uma forma de credencial. Exemplos podem ser sua carteira de motorista, seu cartão de previdência social ou sua certidão de nascimento. Cada um deles contém algumas informações que identificam você e alguma autorização informando que outra pessoa confirmou sua identidade. Alguns certificados, como o seu passaporte, são uma confirmação importante o suficiente da sua identidade para que você não queira perdê-los, para que ninguém os use para se passar por você.
Um certificado digital são dados que funcionam como um certificado físico. Um certificado digital é uma informação incluída na chave pública de uma pessoa que ajuda outras pessoas a verificar se uma chave é genuína ou válida. Os certificados digitais são usados para impedir tentativas de substituir a chave de uma pessoa por outra.
Um certificado digital consiste em três coisas:
● Uma chave pública.
● Informações do certificado. (Informações de "identidade" sobre o usuário, como nome, ID do usuário e assim por diante.) ● Uma ou mais assinaturas digitais.
O objetivo da assinatura digital em um certificado é afirmar que as informações do certificado foram atestadas por alguma outra pessoa ou entidade. A assinatura digital não atesta a autenticidade do certificado como um todo; ele atesta apenas que as informações de identidade assinadas acompanham ou estão vinculadas à chave pública. Assim, um certificado é basicamente uma chave pública com uma ou duas formas de identificação anexadas, além de um forte selo de aprovação de algum outro indivíduo confiável.
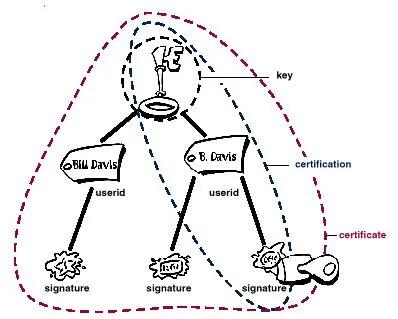 Figura 1-8. Anatomia de um certificado PGP
Figura 1-8. Anatomia de um certificado PGPDistribuição de certificados.
Os certificados são utilizados quando é necessário trocar chaves públicas com outra pessoa. Para pequenos grupos de pessoas que desejam se comunicar com segurança, é fácil trocar manualmente disquetes ou e-mails contendo a chave pública de cada proprietário. Esta é a distribuição manual de chave pública e é prática apenas até certo ponto. Além desse ponto, é necessário implementar sistemas que possam fornecer os mecanismos necessários de segurança, armazenamento e troca para que colegas de trabalho, parceiros de negócios ou estranhos possam se comunicar, se necessário. Eles podem vir na forma de repositórios somente de armazenamento, chamados Servidores de Certificados, ou sistemas mais estruturados que fornecem recursos adicionais de gerenciamento de chaves e são chamados de Infraestruturas de Chave Pública (PKIs).
Servidores de certificados.
Um servidor de certificados, também chamado de servidor certificado ou servidor de chaves, é um banco de dados que permite aos usuários enviar e recuperar certificados digitais. Um servidor certificado geralmente fornece alguns recursos administrativos que permitem que uma empresa mantenha suas políticas de segurança – por exemplo, permitindo que apenas as chaves que atendam a determinados requisitos sejam armazenadas.
Infraestruturas de Chave Pública.
Uma PKI contém os recursos de armazenamento de certificados de um servidor de certificados, mas também fornece recursos de gerenciamento de certificados (a capacidade de emitir, revogar, armazenar, recuperar e confiar em certificados). A principal característica de uma PKI é a introdução do que é conhecido como Autoridade Certificadora,ou CA, que é uma entidade humana — uma pessoa, grupo, departamento, empresa ou outra associação — que uma organização autorizou a emitir certificados para seus usuários de computador. (A função de uma CA é análoga à do Passport Office do governo de um país.) Uma CA cria certificados e os assina digitalmente usando a chave privada da CA. Devido ao seu papel na criação de certificados, a CA é o componente central de uma PKI. Usando a chave pública da CA, qualquer pessoa que queira verificar a autenticidade de um certificado verifica a assinatura digital da CA emissora e, portanto, a integridade do conteúdo do certificado (mais importante ainda, a chave pública e a identidade do titular do certificado).
Formatos de certificado.
Um certificado digital é basicamente uma coleção de informações de identificação vinculadas a uma chave pública e assinadas por um terceiro confiável para provar sua autenticidade. Um certificado digital pode ter vários formatos diferentes.
O PGP reconhece dois formatos de certificado diferentes:
● Certificados PGP ● Certificados X.509 Formato do certificado PGP. Um certificado PGP inclui (mas não está limitado a) as seguintes informações: ● O número da versão do PGP — identifica qual versão do PGP foi usada para criar a chave associada ao certificado. A chave pública do titular do certificado — a parte pública do seu par de chaves, juntamente com o algoritmo da chave: RSA, DH (Diffie-Hellman) ou DSA (Algoritmo de Assinatura Digital).
● As informações do detentor do certificado — consistem em informações de “identidade” sobre o usuário, como seu nome, ID de usuário, fotografia e assim por diante. ● A assinatura digital do proprietário do certificado — também chamada de autoassinatura, é a assinatura que utiliza a chave privada correspondente da chave pública associada ao certificado. ● O período de validade do certificado — a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar. ● O algoritmo de criptografia simétrica preferido para a chave — indica o algoritmo de criptografia para o qual o proprietário do certificado prefere que as informações sejam criptografadas. Os algoritmos suportados são CAST, IDEA ou Triple-DES. Você pode pensar em um certificado PGP como uma chave pública com um ou mais rótulos vinculados a ele (veja a Figura 1.9 ). Nessas 'etiquetas' você encontrará informações que identificam o proprietário da chave e uma assinatura do proprietário da chave, que afirma que a chave e a identificação andam juntas. (Essa assinatura específica é chamada de autoassinatura; todo certificado PGP contém uma autoassinatura.) Um aspecto único do formato de certificado PGP é que um único certificado pode conter múltiplas assinaturas. Várias ou muitas pessoas podem assinar o par chave/identificação para atestar a sua própria garantia de que a chave pública pertence definitivamente ao proprietário especificado. Se você procurar em um servidor de certificados público, poderá notar que certos certificados, como o do criador do PGP, Phil Zimmermann, contêm muitas assinaturas. Alguns certificados PGP consistem em uma chave pública com vários rótulos, cada um contendo um meio diferente de identificar o proprietário da chave (por exemplo, o nome do proprietário e a conta de e-mail corporativa, o apelido do proprietário e a conta de e-mail residencial, uma fotografia do proprietário — tudo em um certificado). A lista de assinaturas de cada uma dessas identidades pode ser diferente; as assinaturas atestam a autenticidade de que um dos rótulos pertence à chave pública, e não que todos os rótulos da chave sejam autênticos. (Observe que 'autêntico' está nos olhos de quem vê - assinaturas são opiniões, e diferentes pessoas dedicam diferentes níveis de devida diligência na verificação da autenticidade antes de assinar uma chave.)
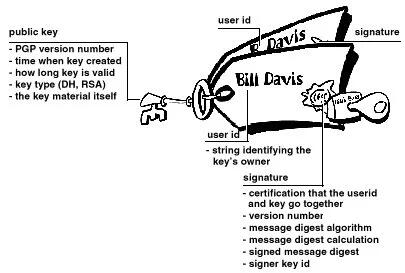 Figura 1-9. Um certificado PGP
Figura 1-9. Um certificado PGPFormato de certificado X.509.
X.509 é outro formato de certificado muito comum. Todos os certificados X.509 estão em conformidade com o padrão internacional ITU-T X.509; assim (teoricamente) os certificados X.509 criados para um aplicativo podem ser usados por qualquer aplicativo compatível com X.509. Na prática, porém, diferentes empresas criaram suas próprias extensões para certificados X.509, e nem todas funcionam juntas. Um certificado exige que alguém valide que uma chave pública e o nome do proprietário da chave andam juntos. Com os certificados PGP, qualquer pessoa pode desempenhar o papel de validador. Com certificados X.509, o validador é sempre uma Autoridade Certificadora ou alguém designado por uma CA. (Tenha em mente que os certificados PGP também suportam totalmente uma estrutura hierárquica usando uma CA para validar certificados.)
Um certificado X.509 é uma coleção de um conjunto padrão de campos contendo informações sobre um usuário ou dispositivo e sua chave pública correspondente. O padrão X.509 define quais informações vão para o certificado e descreve como codificá-lo (o formato dos dados). Todos os certificados X.509 possuem os seguintes dados:
O número da versão X.509
— identifica qual versão do padrão X.509 se aplica a este certificado, o que afeta quais informações podem ser especificadas nele. A mais atual é a versão 3.
A chave pública do titular do certificado
— a chave pública do titular do certificado, juntamente com um identificador de algoritmo que especifica a qual sistema criptográfico a chave pertence e quaisquer parâmetros de chave associados.
O número de série do certificado
— a entidade (aplicação ou pessoa) que criou o certificado é responsável por atribuir-lhe um número de série único para distingui-lo de outros certificados que emite. Esta informação é usada de diversas maneiras; por exemplo, quando um certificado é revogado, seu número de série é colocado em uma Lista de Revogação de Certificados ou CRL.
O identificador exclusivo do detentor do certificado
— (ou DN — nome distinto). Este nome pretende ser exclusivo na Internet. Este nome pretende ser exclusivo na Internet. Um DN consiste em múltiplas subseções e pode ser parecido com isto: CN=Bob Allen, OU=Divisão Total de Segurança de Rede, O=Network Associates, Inc., C=EUA (Referem-se ao nome comum, à unidade organizacional, à organização e ao país do sujeito .)
O período de validade do certificado
— a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar.
O nome exclusivo do emissor do certificado
— o nome exclusivo da entidade que assinou o certificado. Normalmente é uma CA. A utilização do certificado implica confiar na entidade que assinou este certificado. (Observe que em alguns casos, como certificados de CA raiz ou de nível superior , o emissor assina seu próprio certificado.)
A assinatura digital do emitente
— a assinatura utilizando a chave privada da entidade que emitiu o certificado.
O identificador do algoritmo de assinatura
— identifica o algoritmo usado pela CA para assinar o certificado.
Existem muitas diferenças entre um certificado X.509 e um certificado PGP, mas as mais importantes são as seguintes: você pode criar seu próprio certificado PGP;
● você deve solicitar e receber um certificado X.509 de uma autoridade de certificação
● Os certificados X.509 suportam nativamente apenas um único nome para o proprietário da chave
● Os certificados X.509 suportam apenas uma única assinatura digital para atestar a validade da chave
Para obter um certificado X.509, você deve solicitar a uma CA a emissão de um certificado. Você fornece sua chave pública, prova de que possui a chave privada correspondente e algumas informações específicas sobre você. Em seguida, você assina digitalmente as informações e envia o pacote completo – a solicitação de certificado – para a CA. A CA então realiza algumas diligências para verificar se as informações fornecidas estão corretas e, em caso afirmativo, gera o certificado e o devolve.
Você pode pensar em um certificado X.509 como um certificado de papel padrão (semelhante ao que você recebeu ao concluir uma aula de primeiros socorros básicos) com uma chave pública colada nele. Ele contém seu nome e algumas informações sobre você, além da assinatura da pessoa que o emitiu para você.
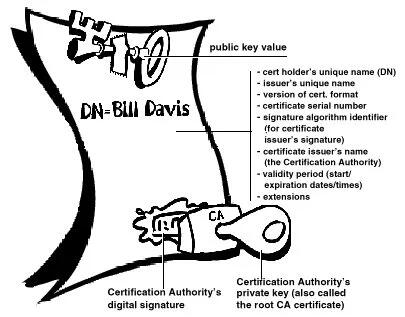
Figura 1-10. Um certificado X.509 Provavelmente, o uso mais visível dos certificados X.509 atualmente é em navegadores da web.
Validade e confiança Cada usuário em um sistema de chave pública está vulnerável a confundir uma chave falsa (certificado) com uma chave real. Validade é a confiança de que um certificado de chave pública pertence ao seu suposto proprietário. A validade é essencial em um ambiente de chave pública onde você deve estabelecer constantemente se um determinado certificado é autêntico ou não. Depois de ter certeza de que um certificado pertencente a outra pessoa é válido, você pode assinar a cópia em seu chaveiro para atestar que verificou o certificado e que ele é autêntico. Se quiser que outras pessoas saibam que você deu ao certificado seu selo de aprovação, você pode exportar a assinatura para um servidor de certificados para que outras pessoas possam vê-la.
Conforme descrito na seção Infraestruturas de Chave Pública , algumas empresas designam uma ou mais Autoridades de Certificação (CAs) para indicar a validade do certificado. Em uma organização que usa uma PKI com certificados X.509, é função da CA emitir certificados aos usuários — um processo que geralmente envolve responder à solicitação de certificado do usuário. Em uma organização que usa certificados PGP sem PKI, é função da CA verificar a autenticidade de todos os certificados PGP e depois assinar os bons. Basicamente, o objetivo principal de uma CA é vincular uma chave pública às informações de identificação contidas no certificado e, assim, garantir a terceiros que algum cuidado foi tomado para garantir que esta ligação das informações de identificação e da chave seja válida. O CA é o Grand Pooh-bah da validação em uma organização; alguém em quem todos confiam e, em algumas organizações, como aquelas que utilizam uma PKI, nenhum certificado é considerado válido, a menos que tenha sido assinado por uma CA confiável.
Verificando validade.
Uma maneira de estabelecer a validade é passar por algum processo manual. Existem várias maneiras de fazer isso. Você pode exigir que o destinatário pretendido lhe entregue fisicamente uma cópia de sua chave pública. Mas isto é muitas vezes inconveniente e ineficiente. Outra forma é verificar manualmente a impressão digital do certificado. Assim como as impressões digitais de cada ser humano são únicas, a impressão digital de cada certificado PGP é única. A impressão digital é um hash do certificado do usuário e aparece como uma das propriedades do certificado. No PGP, a impressão digital pode aparecer como um número hexadecimal ou uma série das chamadas palavras biométricas, que são foneticamente distintas e são usadas para facilitar um pouco o processo de identificação da impressão digital. Você pode verificar se um certificado é válido ligando para o proprietário da chave (para que você origine a transação) e pedindo ao proprietário que leia a impressão digital de sua chave para você e compare essa impressão digital com aquela que você acredita ser a verdadeira. Isso funciona se você conhece a voz do proprietário, mas como verificar manualmente a identidade de alguém que você não conhece? Algumas pessoas colocam a impressão digital de sua chave em seus cartões de visita exatamente por esse motivo. Outra forma de estabelecer a validade do certificado de alguém é confiar que um terceiro indivíduo passou pelo processo de validação do mesmo. Uma CA, por exemplo, é responsável por garantir que, antes de emitir um certificado, ele ou ela o verifique cuidadosamente para ter certeza de que a parte da chave pública realmente pertence ao suposto proprietário. Qualquer pessoa que confie na CA considerará automaticamente quaisquer certificados assinados pela CA como válidos. Outro aspecto da verificação da validade é garantir que o certificado não foi revogado. Para obter mais informações, consulte a seção Revogação de certificado .
Estabelecendo confiança.
Você valida certificados. Você confia nas pessoas. Mais especificamente, você confia nas pessoas para validar os certificados de outras pessoas. Normalmente, a menos que o proprietário lhe entregue o certificado, você terá que confiar na palavra de outra pessoa de que ele é válido.
Introdutores meta e confiáveis.
Na maioria das situações, as pessoas confiam completamente na CA para estabelecer a validade dos certificados. Isso significa que todos os demais dependem da CA para passar por todo o processo de validação manual. Isso é aceitável até um certo número de usuários ou locais de trabalho e, então, não é possível para a AC manter o mesmo nível de validação de qualidade. Nesse caso, é necessário adicionar outros validadores ao sistema.
Um CA também pode ser um meta- introdutor. Um meta-introdutor confere não apenas validade às chaves, mas também confere a capacidade de confiar nas chaves a outros. Semelhante ao rei que entrega seu selo a seus conselheiros de confiança para que eles possam agir de acordo com sua autoridade, o meta-introdutor permite que outros atuem como introdutores de confiança. Esses introdutores confiáveis podem validar chaves com o mesmo efeito do meta-introdutor. Eles não podem, entretanto, criar novos introdutores confiáveis.
Meta-introdutor e introdutor confiável são termos PGP. Em um ambiente X.509, o meta-introdutor é chamado de Autoridade de Certificação raiz ( CA raiz) e os introdutores confiáveis são Autoridades de Certificação subordinadas . A CA raiz usa a chave privada associada a um tipo de certificado especial denominado certificado CA raiz para assinar certificados. Qualquer certificado assinado pelo certificado CA raiz é visto como válido por qualquer outro certificado assinado pela raiz. Este processo de validação funciona mesmo para certificados assinados por outras CAs no sistema — desde que o certificado da CA raiz tenha assinado o certificado da CA subordinada, qualquer certificado assinado pela CA será considerado válido para outras pessoas dentro da hierarquia. Este processo de verificação de backup por meio do sistema para ver quem assinou cujo certificado é chamado de rastreamento de um caminho de certificação ou cadeia de certificação.
Modelos de confiança.
Em sistemas relativamente fechados, como em uma pequena empresa, é fácil rastrear um caminho de certificação até a CA raiz. No entanto, os usuários muitas vezes precisam se comunicar com pessoas fora do seu ambiente corporativo, incluindo algumas que nunca conheceram, como fornecedores, consumidores, clientes, associados e assim por diante. É difícil estabelecer uma linha de confiança com aqueles em quem sua CA não confia explicitamente. As empresas seguem um ou outro modelo de confiança, que determina como os usuários irão estabelecer a validade do certificado. Existem três modelos diferentes:
Confiança Direta.
Confiança Hierárquica Uma teia de confiança Confiança direta A confiança direta é o modelo de confiança mais simples. Neste modelo, um usuário confia que uma chave é válida porque sabe de onde ela veio. Todos os criptosistemas usam essa forma de confiança de alguma forma. Por exemplo, em navegadores da Web, as chaves raiz da Autoridade de Certificação são diretamente confiáveis porque foram enviadas pelo fabricante. Se houver alguma forma de hierarquia, ela se estenderá a partir desses certificados diretamente confiáveis. No PGP, um usuário que valida as chaves e nunca define outro certificado para ser um introdutor confiável está usando confiança direta.
 Figura 1-11. Confiança direta
Figura 1-11. Confiança diretaConfiança Hierárquica.
Em um sistema hierárquico, há vários certificados "raiz" a partir dos quais a confiança se estende. Esses certificados podem certificar eles próprios certificados ou podem certificar certificados que certificam ainda outros certificados em alguma cadeia. Considere isso como uma grande “árvore” de confiança. A validade do certificado "folha" é verificada rastreando desde seu certificador até outros certificadores, até que um certificado raiz diretamente confiável seja encontrado.
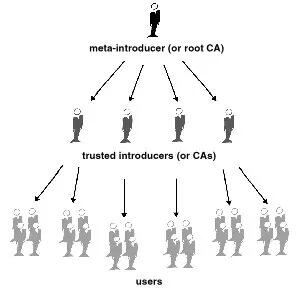
Figura 1-12. Confiança hierárquica
Teia de Confiança.
Uma teia de confiança abrange ambos os outros modelos, mas também acrescenta a noção de que a confiança está nos olhos de quem vê (que é a visão do mundo real) e a ideia de que mais informação é melhor. É, portanto, um modelo de confiança cumulativa. Um certificado pode ser confiável diretamente ou confiável em alguma cadeia que remonta a um certificado raiz diretamente confiável (o meta-introdutor) ou por algum grupo de introdutores.
Talvez você já tenha ouvido falar do termo seis graus de separação, que sugere que qualquer pessoa no mundo pode determinar algum vínculo com qualquer outra pessoa no mundo usando seis ou menos outras pessoas como intermediários. Esta é uma teia de introdutores. É também a visão de confiança do PGP. PGP usa assinaturas digitais como forma de introdução. Quando qualquer usuário assina a chave de outro, ele ou ela se torna o introdutor dessa chave. À medida que esse processo avança, ele estabelece uma rede de confiança.
Em um ambiente PGP, qualquer usuário pode atuar como autoridade certificadora. Qualquer usuário PGP pode validar o certificado de chave pública de outro usuário PGP. No entanto, tal certificado só é válido para outro usuário se a parte confiável reconhecer o validador como um introdutor confiável. (Ou seja, você confia na minha opinião de que as chaves dos outros são válidas apenas se você me considerar um apresentador confiável. Caso contrário, minha opinião sobre a validade das outras chaves é discutível.) Armazenados no chaveiro público de cada usuário estão indicadores de
● se o usuário considera ou não uma chave específica válida
● o nível de confiança que o usuário deposita na chave que o proprietário da chave pode servir como certificador das chaves de terceiros
Você indica, na sua cópia da minha chave, se acha que meu julgamento conta. Na verdade, é um sistema de reputação: certas pessoas têm a reputação de fornecer boas assinaturas e as pessoas confiam nelas para atestar a validade de outras chaves.
Níveis de confiança no PGP.
O nível mais alto de confiança em uma chave, a confiança implícita , é a confiança em seu próprio par de chaves. O PGP assume que se você possui a chave privada, você deve confiar nas ações da sua chave pública relacionada. Quaisquer chaves assinadas pela sua chave implicitamente confiável são válidas.
Existem três níveis de confiança que você pode atribuir à chave pública de outra pessoa:
● Confiança total ● Confiança marginal ● Não confiável (ou não confiável)
Para tornar as coisas confusas, também existem três níveis de validade:
● Válido ● Marginalmente válido ● Inválido
Para definir a chave de outra pessoa como um introdutor confiável, você
- Comece com uma chave válida, que seja.
- assinado por você ou
-
assinado por outro apresentador confiável e então
-
Defina o nível de confiança que você acha que o proprietário da chave tem direito.
Por exemplo, suponha que seu chaveiro contenha a chave de Alice. Você validou a chave de Alice e indica isso assinando-a. Você sabe que Alice é uma verdadeira defensora da validação de chaves de outras pessoas. Portanto, você atribui a chave dela com confiança total. Isso faz de Alice uma Autoridade Certificadora. Se Alice assinar a chave de outra pessoa, ela aparecerá como Válida em seu chaveiro. O PGP requer uma assinatura Totalmente confiável ou duas assinaturas Marginalmente confiáveis para estabelecer uma chave como válida. O método do PGP de considerar dois Marginais iguais a um Completo é semelhante a um comerciante que solicita duas formas de identificação. Você pode considerar Alice bastante confiável e também considerar Bob bastante confiável. Qualquer um deles sozinho corre o risco de assinar acidentalmente uma chave falsificada, portanto, você pode não depositar total confiança em nenhum deles. No entanto, as probabilidades de ambos os indivíduos terem assinado a mesma chave falsa são provavelmente pequenas.
Revogação de certificado.
Os certificados só são úteis enquanto são válidos. Não é seguro simplesmente presumir que um certificado é válido para sempre. Na maioria das organizações e em todas as PKIs, os certificados têm uma vida útil restrita. Isso restringe o período em que um sistema fica vulnerável caso ocorra um comprometimento do certificado.
Os certificados são assim criados com um período de validade programado: uma data/hora de início e uma data/hora de expiração. Espera-se que o certificado seja utilizável durante todo o seu período de validade (seu tempo de vida ). Quando o certificado expirar, ele não será mais válido, pois a autenticidade do seu par chave/identificação não estará mais garantida. (O certificado ainda pode ser usado com segurança para reconfirmar informações que foram criptografadas ou assinadas dentro do período de validade – no entanto, ele não deve ser confiável para tarefas criptográficas futuras.)
Existem também situações em que é necessário invalidar um certificado antes da sua data de expiração, como quando o titular do certificado termina o contrato de trabalho com a empresa ou suspeita que a chave privada correspondente do certificado foi comprometida. Isso é chamado de revogação. Um certificado revogado é muito mais suspeito do que um certificado expirado. Os certificados expirados são inutilizáveis, mas não apresentam a mesma ameaça de comprometimento que um certificado revogado. Qualquer pessoa que tenha assinado um certificado pode revogar a sua assinatura no certificado (desde que utilize a mesma chave privada que criou a assinatura). Uma assinatura revogada indica que o signatário não acredita mais que a chave pública e as informações de identificação pertencem uma à outra, ou que a chave pública do certificado (ou a chave privada correspondente) foi comprometida. Uma assinatura revogada deve ter quase tanto peso quanto um certificado revogado. Com certificados X.509, uma assinatura revogada é praticamente igual a um certificado revogado, visto que a única assinatura no certificado é aquela que o tornou válido em primeiro lugar – a assinatura da CA. Os certificados PGP fornecem o recurso adicional de que você pode revogar todo o seu certificado (não apenas as assinaturas nele) se você achar que o certificado foi comprometido. Somente o proprietário do certificado (o detentor da chave privada correspondente) ou alguém que o proprietário do certificado tenha designado como revogador pode revogar um certificado PGP. (Designar um revogador é uma prática útil, pois muitas vezes é a perda da senha da chave privada correspondente do certificado que leva um usuário PGP a revogar seu certificado - uma tarefa que só é possível se alguém tiver acesso à chave privada. ) Somente o emissor do certificado pode revogar um certificado X.509.
Comunicar que um certificado foi revogado.
Quando um certificado é revogado, é importante conscientizar os usuários potenciais do certificado de que ele não é mais válido. Com certificados PGP, a maneira mais comum de comunicar que um certificado foi revogado é publicá-lo em um servidor de certificados para que outras pessoas que desejem se comunicar com você sejam avisadas para não usar essa chave pública. Em um ambiente PKI, a comunicação de certificados revogados é mais comumente obtida por meio de uma estrutura de dados chamada Lista de Revogação de Certificados, ou CRL, que é publicada pela CA. A CRL contém uma lista validada com carimbo de data e hora de todos os certificados revogados e não expirados no sistema. Os certificados revogados permanecem na lista apenas até expirarem e, em seguida, são removidos da lista — isso evita que a lista fique muito longa. A CA distribui a CRL aos usuários em algum intervalo programado regularmente (e potencialmente fora do ciclo, sempre que um certificado é revogado). Teoricamente, isso impedirá que os usuários usem involuntariamente um certificado comprometido. É possível, no entanto, que haja um período de tempo entre as CRLs em que um certificado recentemente comprometido seja usado.
O que é uma senha?
A maioria das pessoas está familiarizada com a restrição de acesso a sistemas de computador por meio de uma senha, que é uma sequência única de caracteres que um usuário digita como código de identificação.
Uma senha longa é uma versão mais longa de uma senha e, em teoria, mais segura. Normalmente composta por várias palavras, uma frase secreta é mais segura contra ataques de dicionário padrão, em que o invasor tenta todas as palavras do dicionário na tentativa de determinar sua senha. As melhores senhas são relativamente longas e complexas e contêm uma combinação de letras maiúsculas e minúsculas, caracteres numéricos e de pontuação. O PGP usa uma senha para criptografar sua chave privada em sua máquina. Sua chave privada é criptografada em seu disco usando um hash de sua senha como chave secreta. Você usa a senha para descriptografar e usar sua chave privada. Uma senha deve ser difícil de esquecer e difícil de ser adivinhada por outras pessoas. Deve ser algo já firmemente enraizado na sua memória de longo prazo, em vez de algo que você invente do zero. Por que? Porque se você esquecer sua senha, você estará sem sorte. Sua chave privada é total e absolutamente inútil sem sua senha e nada pode ser feito a respeito. Lembra-se da citação anterior neste capítulo?
 PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.
PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.Divisão de chave.
Dizem que um segredo não é segredo se for conhecido por mais de uma pessoa. Compartilhar um par de chaves privadas representa um grande problema. Embora não seja uma prática recomendada, às vezes é necessário compartilhar um par de chaves privadas. Chaves de assinatura corporativa, por exemplo, são chaves privadas usadas por uma empresa para assinar – por exemplo – documentos legais, informações pessoais confidenciais ou comunicados de imprensa para autenticar sua origem. Nesse caso, vale a pena que vários membros da empresa tenham acesso à chave privada. No entanto, isto significa que qualquer indivíduo pode agir plenamente em nome da empresa. Nesse caso, é aconselhável dividir a chave entre várias pessoas, de modo que mais de uma ou duas pessoas apresentem um pedaço da chave para reconstituí-la em condições utilizáveis. Se poucas peças da chave estiverem disponíveis, a chave ficará inutilizável. Alguns exemplos são dividir uma chave em três partes e exigir duas delas para reconstituir a chave, ou dividi-la em duas partes e exigir ambas as peças. Se uma conexão de rede segura for usada durante o processo de reconstituição, os acionistas da chave não precisam estar fisicamente presentes para aderirem novamente à chave.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28SummaDB
This was a hierarchical database server similar to the original Firebase. Records were stored on a LevelDB on different paths, like:
/fruits/banana/color:yellow/fruits/banana/flavor:sweet
And could be queried by path too, using HTTP, for example, a call to
http://hostname:port/fruits/banana, for example, would return a JSON document likejson { "color": "yellow", "flavor": "sweet" }While a call to
/fruitswould returnjson { "banana": { "color": "yellow", "flavor": "sweet" } }POST,PUTandPATCHrequests also worked.In some cases the values would be under a special
"_val"property to disambiguate them from paths. (I may be missing some other details that I forgot.)GraphQL was also supported as a query language, so a query like
graphql query { fruits { banana { color } } }would return
{"fruits": {"banana": {"color": "yellow"}}}.SummulaDB
SummulaDB was a browser/JavaScript build of SummaDB. It ran on the same Go code compiled with GopherJS, and using PouchDB as the storage backend, if I remember correctly.
It had replication between browser and server built-in, and one could replicate just subtrees of the main tree, so you could have stuff like this in the server:
json { "users": { "bob": {}, "alice": {} } }And then only allow Bob to replicate
/users/boband Alice to replicate/users/alice. I am sure the require auth stuff was also built in.There was also a PouchDB plugin to make this process smoother and data access more intuitive (it would hide the
_valstuff and allow properties to be accessed directly, today I wouldn't waste time working on these hidden magic things).The computed properties complexity
The next step, which I never managed to get fully working and caused me to give it up because of the complexity, was the ability to automatically and dynamically compute materialized properties based on data in the tree.
The idea was partly inspired on CouchDB computed views and how limited they were, I wanted a thing that would be super powerful, like, given
json { "matches": { "1": { "team1": "A", "team2": "B", "score": "2x1", "date": "2020-01-02" }, "1": { "team1": "D", "team2": "C", "score": "3x2", "date": "2020-01-07" } } }One should be able to add a computed property at
/matches/standingsthat computed the scores of all teams after all matches, for example.I tried to complete this in multiple ways but they were all adding much more complexity I could handle. Maybe it would have worked better on a more flexible and powerful and functional language, or if I had more time and patience, or more people.
Screenshots
This is just one very simple unfinished admin frontend client view of the hierarchical dataset.

- https://github.com/fiatjaf/summadb
- https://github.com/fiatjaf/summuladb
- https://github.com/fiatjaf/pouch-summa
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Parallel Chains
We want merged-mined blockchains. We want them because it is possible to do things in them that aren't doable in the normal Bitcoin blockchain because it is rightfully too expensive, but there are other things beside the world money that could benefit from a "distributed ledger" -- just like people believed in 2013 --, like issued assets and domain names (just the most obvious examples).
On the other hand we can't have -- like people believed in 2013 -- a copy of Bitcoin for every little idea with its own native token that is mined by proof-of-work and must get off the ground from being completely valueless into having some value by way of a miracle that operated only once with Bitcoin.
It's also not a good idea to have blockchains with custom merged-mining protocol (like Namecoin and Rootstock) that require Bitcoin miners to run their software and be an active participant and miner for that other network besides Bitcoin, because it's too cumbersome for everybody.
Luckily Ruben Somsen invented this protocol for blind merged-mining that solves the issue above. Although it doesn't solve the fact that each parallel chain still needs some form of "native" token to pay miners -- or it must use another method that doesn't use a native token, such as trusted payments outside the chain.
How does it work
With the
SIGHASH_NOINPUT/SIGHASH_ANYPREVOUTsoft-fork[^eltoo] it becomes possible to create presigned transactions that aren't related to any previous UTXO.Then you create a long sequence of transactions (sufficient to last for many many years), each with an
nLockTimeof 1 and each spending the next (you create them from the last to the first). Since theirscriptSig(the unlocking script) will useSIGHASH_ANYPREVOUTyou can obtain a transaction id/hash that doesn't include the previous TXO, you can, for example, in a sequence of transactionsA0-->B(B spends output 0 from A), include the signature for "spending A0 on B" inside thescriptPubKey(the locking script) of "A0".With the contraption described above it is possible to make that long string of transactions everybody will know (and know how to generate) but each transaction can only be spent by the next previously decided transaction, no matter what anyone does, and there always must be at least one block of difference between them.
Then you combine it with
RBF,SIGHASH_SINGLEandSIGHASH_ANYONECANPAYso parallel chain miners can add inputs and outputs to be able to compete on fees by including their own outputs and getting change back while at the same time writing a hash of the parallel block in the change output and you get everything working perfectly: everybody trying to spend the same output from the long string, each with a different parallel block hash, only the highest bidder will get the transaction included on the Bitcoin chain and thus only one parallel block will be mined.See also
[^eltoo]: The same thing used in Eltoo.
-
 @ 9bcc5462:eb501d90
2025-02-24 17:47:28
@ 9bcc5462:eb501d90
2025-02-24 17:47:28Every generation loves to learn. However, our public schooling system has gone as far as it can take us. The abundance of easily accessible information on the internet, coupled with emerging tech like AI, decentralized protocols and bitcoin, means this is our time to innovate our learning infrastructure. A complete overhaul is due along with the development of a pilot program to test new and unconventional models.
Let’s carve a path towards innovation by sparking discussion around this topic. Hence, this blueprint. It is a gauntlet for any person who genuinely wants to become a stakeholder for our country’s future. Entry points are:
- Builders—Startups, developers and investors who will fund and create infrastructure.
- Practitioners—Educators and researchers who will test models.
- Supporters—Parents, donors and community members who want to contribute.
Where Do We Begin?
Let’s think about crafting the main components of a new pilot model. Below are suggested areas of focus:
- DEFINITION
- APPROACH
- PHILOSOPHY
- CULTURE
- PHYSICAL DESIGN
- OPERATIONAL ORGANIZATION
- ACCOUNTABILITY METHODS
- RISKS & CHALLENGES
- STYLE
- STAKEHOLDERS
How It Works
After researching your pedagogical ideas for current and future generations of scholars, it’s time to share your insights. Contribute your viewpoint by structuring a blueprint—one page per section—in the following sequence:
- Definition of your modern learning model with its key principles.
- Description of the core learning approach.
- Philosophy distilled into central concepts that will orient stakeholders.
- Culture your modern learning model aspires to live by.
- Potential challenges, risks and drawbacks.
- Design of physical spaces and rationale.
- Operational framework detailing adult and child learning organization.
- Accountability methods to ensure skill growth and competency.
- Style development and name of your model.
- Skin in the game, sign your model with your first and last name (unite stakeholders).
Perhaps if enough stakeholders come together, we can begin to actualize a more effective and updated way of learning. This is a challenge meant to separate those willing to engage in discourse, planning and laying foundations from those content to complain from the sidelines.
Why Now and Where Does the Money Come From?
After being a public educator for fifteen years, I learned you will not change the system, the system will change you. It’s time to design and build above and apart from the current model. 2025 is when courageous people step up to the plate and discuss our learning infrastructure. Whether it’s contributing out of the box thinking, modernizing curriculum, investing in startups or creating your own venture; there is no greater time than now. And no greater place than in the USA!
(By extension, we also create the opportunity to influence our global allies including our neighbors to the North and South.)
“But how!?” Learning Producers is figuring it out by asking not, “how?” but “who?” Who will unite together to develop our learning infrastructure? If you decide you want to participate and join our efforts, share your blueprint as well. For all stakeholders, this is an investment in an untapped market of a new learning economy.
If not, you’re not alone. Some consider this just rhetoric, idealism, or wishful thinking. Additionally, it is unclear how such actions can be profitable or how such infrastructure building will be funded. Money talks. Bullshit walks, right? In that case, let’s talk, and let’s fine tune our BS detectors. Onward, with this call to action:
- Share your own blueprint online or reach out to Learning Producers, Inc. (Learningproducers.com).
- Conduct research on an ideal location and team to lay foundations on a pilot program at small scale.
- Engage in dialogue with investors interested in developing learning infrastructure for their own children and families.
- Secure stakeholders to develop and test a real world pilot model (real location, real agreements, real timeline, real people).
- Sponsor or donate resources to counter concerns over funding.
Now, we leave you with our blueprint:
PEDAGOGICAL WABI-SABI
We hope you enjoy it.
Sincerely,
Israel Hernandez
Founder of Learning Producers
**[Read or download full blueprint here: https://www.learningproducers.com/blog/pedagogical-wabi-sabiblueprint-for-developing-learning-infrastructure ]
-
 @ c631e267:c2b78d3e
2025-03-31 07:23:05
@ c631e267:c2b78d3e
2025-03-31 07:23:05Der Irrsinn ist bei Einzelnen etwas Seltenes – \ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel. \ Friedrich Nietzsche
Erinnern Sie sich an die Horrorkomödie «Scary Movie»? Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

Diese Szene kommt mir automatisch in den Sinn, wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
Die Europäische Union hat sich selbst über Jahre konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
In den USA haben sich die Vorzeichen allerdings mittlerweile geändert, und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
Statt jedoch umzukehren oder wenigstens zu bremsen und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die Kommentatoren des Events gegenseitig in sensationslüsterner «Berichterstattung».
Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen, Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, selbstzerstörerischen Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», erklärte die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
Zusätzlich brisant ist, dass aktuell «die ganze EU von Deutschen regiert wird», wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
Es wird dringend Zeit, dass wir, der Souverän, diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts den Frieden auszurufen. Seien wir dabei!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28OP_CHECKTEMPLATEVERIFYand the "covenants" dramaThere are many ideas for "covenants" (I don't think this concept helps in the specific case of examining proposals, but fine). Some people think "we" (it's not obvious who is included in this group) should somehow examine them and come up with the perfect synthesis.
It is not clear what form this magic gathering of ideas will take and who (or which ideas) will be allowed to speak, but suppose it happens and there is intense research and conversations and people (ideas) really enjoy themselves in the process.
What are we left with at the end? Someone has to actually commit the time and put the effort and come up with a concrete proposal to be implemented on Bitcoin, and whatever the result is it will have trade-offs. Some great features will not make into this proposal, others will make in a worsened form, and some will be contemplated very nicely, there will be some extra costs related to maintenance or code complexity that will have to be taken. Someone, a concreate person, will decide upon these things using their own personal preferences and biases, and many people will not be pleased with their choices.
That has already happened. Jeremy Rubin has already conjured all the covenant ideas in a magic gathering that lasted more than 3 years and came up with a synthesis that has the best trade-offs he could find. CTV is the result of that operation.
The fate of CTV in the popular opinion illustrated by the thoughtless responses it has evoked such as "can we do better?" and "we need more review and research and more consideration of other ideas for covenants" is a preview of what would probably happen if these suggestions were followed again and someone spent the next 3 years again considering ideas, talking to other researchers and came up with a new synthesis. Again, that person would be faced with "can we do better?" responses from people that were not happy enough with the choices.
And unless some famous Bitcoin Core or retired Bitcoin Core developers were personally attracted by this synthesis then they would take some time to review and give their blessing to this new synthesis.
To summarize the argument of this article, the actual question in the current CTV drama is that there exists hidden criteria for proposals to be accepted by the general community into Bitcoin, and no one has these criteria clear in their minds. It is not as simple not as straightforward as "do research" nor it is as humanly impossible as "get consensus", it has a much bigger social element into it, but I also do not know what is the exact form of these hidden criteria.
This is said not to blame anyone -- except the ignorant people who are not aware of the existence of these things and just keep repeating completely false and unhelpful advice for Jeremy Rubin and are not self-conscious enough to ever realize what they're doing.
-
 @ 94a6a78a:0ddf320e
2025-02-19 21:10:15
@ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables decentralized, censorship-resistant communication. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on users, developers, and relay operators.
If you believe in free speech, decentralization, and an open internet, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, every effort helps build a more robust network.
Here’s how you can get involved and make a difference.
1️⃣ Use Nostr Daily
The simplest and most effective way to contribute to Nostr is by using it regularly. The more active users, the stronger and more valuable the network becomes.
✅ Post, comment, and zap (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ Engage with new users and help them understand how Nostr works.\ ✅ Try different Nostr clients like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience.
Your activity keeps the network alive and helps encourage more developers and relay operators to invest in the ecosystem.
2️⃣ Run Your Own Nostr Relay
Relays are the backbone of Nostr, responsible for distributing messages across the network. The more independent relays exist, the stronger and more censorship-resistant Nostr becomes.
✅ Set up your own relay to help decentralize the network further.\ ✅ Experiment with relay configurations and different performance optimizations.\ ✅ Offer public or private relay services to users looking for high-quality infrastructure.
If you're not technical, you can still support relay operators by subscribing to a paid relay or donating to open-source relay projects.
3️⃣ Support Paid Relays & Infrastructure
Free relays have helped Nostr grow, but they struggle with spam, slow speeds, and sustainability issues. Paid relays help fund better infrastructure, faster message delivery, and a more reliable experience.
✅ Subscribe to a paid relay to help keep it running.\ ✅ Use premium services like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ Donate to relay operators who invest in long-term infrastructure.
By funding Nostr’s decentralized backbone, you help ensure its longevity and reliability.
4️⃣ Zap Developers, Creators & Builders
Many people contribute to Nostr without direct financial compensation—developers who build clients, relay operators, educators, and content creators. You can support them with zaps! ⚡
✅ Find developers working on Nostr projects and send them a zap.\ ✅ Support content creators and educators who spread awareness about Nostr.\ ✅ Encourage builders by donating to open-source projects.
Micro-payments via the Lightning Network make it easy to directly support the people who make Nostr better.
5️⃣ Develop New Nostr Apps & Tools
If you're a developer, you can build on Nostr’s open protocol to create new apps, bots, or tools. Nostr is permissionless, meaning anyone can develop for it.
✅ Create new Nostr clients with unique features and user experiences.\ ✅ Build bots or automation tools that improve engagement and usability.\ ✅ Experiment with decentralized identity, authentication, and encryption to make Nostr even stronger.
With no corporate gatekeepers, your projects can help shape the future of decentralized social media.
6️⃣ Promote & Educate Others About Nostr
Adoption grows when more people understand and use Nostr. You can help by spreading awareness and creating educational content.
✅ Write blogs, guides, and tutorials explaining how to use Nostr.\ ✅ Make videos or social media posts introducing new users to the protocol.\ ✅ Host discussions, Twitter Spaces, or workshops to onboard more people.
The more people understand and trust Nostr, the stronger the ecosystem becomes.
7️⃣ Support Open-Source Nostr Projects
Many Nostr tools and clients are built by volunteers, and open-source projects thrive on community support.
✅ Contribute code to existing Nostr projects on GitHub.\ ✅ Report bugs and suggest features to improve Nostr clients.\ ✅ Donate to developers who keep Nostr free and open for everyone.
If you're not a developer, you can still help with testing, translations, and documentation to make projects more accessible.
🚀 Every Contribution Strengthens Nostr
Whether you:
✔️ Post and engage daily\ ✔️ Zap creators and developers\ ✔️ Run or support relays\ ✔️ Build new apps and tools\ ✔️ Educate and onboard new users
Every action helps make Nostr more resilient, decentralized, and unstoppable.
Nostr isn’t just another social network—it’s a movement toward a free and open internet. If you believe in digital freedom, privacy, and decentralization, now is the time to get involved.
-
 @ 78c90fc4:4bff983c
2025-03-31 07:03:41
@ 78c90fc4:4bff983c
2025-03-31 07:03:41In Palästina und im Ausland wurde das Abkommen einzelner jüdischer Organisationen mit dem nationalsozialistischen Deutschland heftig kritisiert. Auf dem 18. Zionistenkongress 1933 in Prag etwa bezeichnete der Schriftsteller Schalom Asch das Abkommen mit Hitlers Regime als „Verrat am Weltjudentum“. Chaim Arlosoroff, der damalige Verhandlungsführer der Jewish Agency, wurde wahrscheinlich deshalb im Juni 1933 Opfer eines Mordanschlags.
https\://de.m.wikipedia.org/wiki/Ha’avara-Abkommen
Am 16. Juni 1933 wurde Chaim Arlosoroff kurz nach seiner Rückkehr von den Transfer-Verhandlungen in Deutschland durch den Pistolenschuss eines Attentäters schwer verletzt, als er mit seiner Frau Sima, geb. Rubin, am Strand von Tel Aviv entlangging. Er verstarb am folgenden Tag im Krankenhaus. Wer der Attentäter war, ist bis heute ungeklärt. Zunächst wurden drei Verdächtige angeklagt. Zwei von ihnen wurden freigesprochen, einer, Abraham Stavsky, wurde verurteilt, doch das Urteil wurde durch das oberste Appellationsgericht aufgehoben.
https://de.m.wikipedia.org/wiki/Chaim_Arlosoroff#Ermordung
Instrumentalisierung des Holocaust
Von Anneliese Fikentscher und Andreas Neumann
Zum Schluss ein Zitat aus dem 2017 erschienenen Buch "Die israelisch-jüdische Tragödie. Von Auschwitz zum Besatzungs- und Apartheidstaat. Das Ende der Verklärung" von Arn Strohmeyer: „Der vielleicht radikalste Kritiker des israelischen Holocaustgedenkens ist der amerikanisch -jüdische Politologe Norman Finkelstein. Er wendet sich vor allem gegen das in Israel und den USA verwendete Dogma, der Holocaust sei 'einzigartig' gewesen und mit anderen Verbrechen nicht vergleichbar, dass er in der Geschichte also ohne Parallele sei. Diese Behauptung – so Finkelstein – impliziert eine Reihe anderer Behauptungen, die wiederum die Instrumentalisierung des Holocaust ausmachen. Erstens: Die Konstruktion des Holocaust als einzigartig gilt als gegeben, sie zu leugnen gilt als Leugnung des Holocaust. Diese Behauptung schließt zweitens ein rationales Verständnis des Holocaust aus, er macht den Holocaust zu einem Mysterium, wie Elie Wiesel ihn verstanden hat. Einzigartiges Leid verleiht drittens einen einzigartigen Anspruch. Die Unvergleichlichkeit des Holocaust stellt also ein moralisches Kapital dar, das Israel als politisches Alibi benutzt. Israel kann – so Finkelstein – diese moralischen und emotionalen Ansprüche an andere Staaten stellen und die Anerkennung seines Rechts einfordern, dass es als besonders bedroht gelten kann und seine Anstrengungen zum Überleben der Unterstützung bedarf. Die Behauptung der Einzigartigkeit des Holocaust beinhaltet auch die Behauptung der jüdischen Einzigartigkeit. Der Holocaust ist also etwas Besonderes, weil Juden etwas Besonderes sind, was man als säkularisierte Version der Auserwähltheit deuten kann. Diese Behauptungen – so Finkelstein – sollen Israels Sonderstellung legitimieren, sollen von vornherein jede unmenschliche Behandlung von Nichtjuden entschuldigen (Israel ist 'alles erlaubt!') und machen diesen Staat und seine Politik gegen jede Kritik immun. Bei dieser Instrumentalisierung des Holocaust bleiben die Rechte und die Würde der Opfer – welcher auch immer – völlig auf der Strecke.“ Ist das einer breiten Öffentlichkeit bewusst?
http://www.nrhz.de/flyer/beitrag.php?id=24469
Perplexity:
Der Schriftsteller Schalom Asch kritisierte das Ha'avara-Abkommen scharf auf dem 18. Zionistischen Kongress, der vom 21. August bis 4. September 1933 in Prag stattfand. Er bezeichnete das Abkommen mit dem Hitler-Regime als "ein Verrat am Weltjudentum"[1][2].
Das Ha'avara-Abkommen wurde am 10. August 1933 zwischen der Jewish Agency, der Zionistischen Vereinigung für Deutschland und dem deutschen Reichsministerium für Wirtschaft geschlossen. Es sollte die Emigration deutscher Juden nach Palästina erleichtern und gleichzeitig den deutschen Export fördern[2].
Am 5. November 1933 wurde die "Trust and Transfer Office Ha'avara Ltd." als quasi privates Unternehmen eingetragen[1][3]. Trotz der anfänglichen Kritik billigte die Zionistische Weltorganisation auf ihrer Konferenz am 20. August 1935 in Luzern mit Mehrheit den Ha'avara-Abschluss und übernahm sogar dessen gesamte Tätigkeit in eigene Regie[1][2][3].
Das Abkommen war innerhalb der zionistischen Bewegung umstritten, da es den gleichzeitig vorangetriebenen Boykottmaßnahmen gegen die Nationalsozialisten zuwiderlief[2]. Es ermöglichte deutschen Juden, einen Teil ihres Vermögens nach Palästina zu transferieren, wobei ein bestimmter Prozentsatz als Reichsfluchtsteuer vom deutschen Fiskus einbehalten wurde[5].
Quellen
[1] Zionistenkongress - Wikiwand https\://www.wikiwand.com/de/articles/Zionistenkongress
[2] Ha'avara-Abkommen - Wikiwand https\://www.wikiwand.com/de/articles/Haavara-Abkommen
[3] Zionistenkongress - Wikipedia https\://de.wikipedia.org/wiki/Zionistenkongress
[4] Schalom Asch - Wikipedia https\://de.wikipedia.org/wiki/Schalom_Asch
[5] Ha'avara-Abkommen - Wikipedia https\://de.wikipedia.org/wiki/Ha%E2%80%99avara-Abkommen
[6] Stefan Zweig. Briefe zum Judentum. Hg. v. Stefan Litt. Berlin ... https\://judaica.ch/article/view/8320/11519
[7] Das Haavara-Transfer-Abkommen | Die Wohnung | bpb.de https\://www.bpb.de/themen/nationalsozialismus-zweiter-weltkrieg/die-wohnung/195259/das-haavara-transfer-abkommen/
[8] Jüdischer Verlag - Wikipedia https\://de.wikipedia.org/wiki/J%C3%BCdischer_Verlag
Artikel https://x.com/RealWsiegrist/status/1906601705355252211
-
 @ bc52210b:20bfc6de
2025-04-28 20:13:25
@ bc52210b:20bfc6de
2025-04-28 20:13:25
Imagine a world where clean, safe, and efficient nuclear power can be delivered to any corner of the globe, powering everything from small villages to bustling cities. This vision is becoming a reality with the development of nuclear modular plants—compact, portable nuclear reactors that can be shipped in standard containers and set up quickly to provide reliable energy. These innovative power sources use fission—the process of splitting atomic nuclei to release energy, the same fundamental principle that powers traditional nuclear plants—but with a twist: they utilize thorium as fuel and a molten salt system for cooling and fuel delivery. This combination offers a host of benefits that could revolutionize how we think about nuclear energy.
Portability and Deployment
One of the most significant advantages of these nuclear modular plants is their portability. Designed to fit within standard shipping containers, these reactors can be transported by truck, ship, or even air to virtually any location. This makes them ideal for remote communities, disaster relief efforts, or military operations where traditional power infrastructure is lacking or damaged. Setting up a conventional power plant typically takes years, but these modular units can be operational in a matter of weeks, providing a rapid solution to energy needs.
Safety Features
Safety is a paramount concern in nuclear energy, and modular thorium molten salt reactors (MSRs) offer several inherent safety advantages. Unlike traditional reactors that use water under high pressure, MSRs operate at atmospheric pressure, eliminating the risk of pressure-related accidents. The fuel is dissolved in the molten salt, which means there's no solid fuel that could melt down. If the reactor overheats, the salt expands, naturally slowing the fission reaction—a built-in safety mechanism. Additionally, thorium-based fuels produce less long-lived radioactive waste, reducing the long-term environmental impact.
Efficiency and Abundance
Thorium is a more abundant resource than uranium, with estimates suggesting it is three to four times more plentiful in the Earth's crust. This abundance makes thorium a sustainable fuel choice for the future. Moreover, MSRs can operate at higher temperatures than traditional reactors, leading to greater thermal efficiency. This means more electricity can be generated from the same amount of fuel, making the energy production process more efficient and cost-effective in the long run.
Scalability
The modular design of these reactors allows for scalability to meet varying power demands. A single unit might power a small community, while multiple units can be combined to serve larger towns or cities. This flexibility is particularly useful for growing populations or regions with fluctuating energy needs. As demand increases, additional modules can be added without the need for extensive new infrastructure.
Cost-Effectiveness
While the initial investment in nuclear modular plants may be significant, the long-term operational costs can be lower than traditional power sources. The high efficiency of MSRs means less fuel is needed over time, and the reduced waste production lowers disposal costs. Additionally, the ability to mass-produce these modular units could drive down manufacturing costs, making nuclear power more accessible and affordable.
Environmental Impact
Nuclear power is already one of the cleanest energy sources in terms of carbon emissions, and thorium MSRs take this a step further. By producing less long-lived waste and utilizing a more abundant fuel, these reactors offer a more sustainable path for nuclear energy. Furthermore, their ability to provide reliable baseload power can help reduce reliance on fossil fuels, contributing to global efforts to combat climate change.
Challenges and Considerations
Despite these benefits, there are challenges to overcome before nuclear modular plants can be widely deployed. The technology for thorium MSRs is still in the developmental stage, with ongoing research needed to address issues such as material corrosion and fuel processing. Regulatory frameworks will also need to adapt to this new type of reactor, and public perception of nuclear energy remains a hurdle in many regions. However, with continued investment and innovation, these obstacles can be addressed.
Conclusion
In conclusion, nuclear modular plants using thorium and molten salt systems represent a promising advancement in nuclear technology. Their portability, safety features, efficiency, scalability, and environmental benefits make them an attractive option for meeting the world's growing energy needs. While challenges remain, the potential of these reactors to provide clean, reliable power to communities around the globe is undeniable. As research and development continue, we may soon see a new era of nuclear energy that is safer, more efficient, and more accessible than ever before.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A response to Achim Warner's "Drivechain brings politics to miners" article
I mean this article: https://achimwarner.medium.com/thoughts-on-drivechain-i-miners-can-do-things-about-which-we-will-argue-whether-it-is-actually-a5c3c022dbd2
There are basically two claims here:
1. Some corporate interests might want to secure sidechains for themselves and thus they will bribe miners to have these activated
First, it's hard to imagine why they would want such a thing. Are they going to make a proprietary KYC chain only for their users? They could do that in a corporate way, or with a federation, like Facebook tried to do, and that would provide more value to their users than a cumbersome pseudo-decentralized system in which they don't even have powers to issue currency. Also, if Facebook couldn't get away with their federated shitcoin because the government was mad, what says the government won't be mad with a sidechain? And finally, why would Facebook want to give custody of their proprietary closed-garden Bitcoin-backed ecosystem coins to a random, open and always-changing set of miners?
But even if they do succeed in making their sidechain and it is very popular such that it pays miners fees and people love it. Well, then why not? Let them have it. It's not going to hurt anyone more than a proprietary shitcoin would anyway. If Facebook really wants a closed ecosystem backed by Bitcoin that probably means we are winning big.
2. Miners will be required to vote on the validity of debatable things
He cites the example of a PoS sidechain, an assassination market, a sidechain full of nazists, a sidechain deemed illegal by the US government and so on.
There is a simple solution to all of this: just kill these sidechains. Either miners can take the money from these to themselves, or they can just refuse to engage and freeze the coins there forever, or they can even give the coins to governments, if they want. It is an entirely good thing that evil sidechains or sidechains that use horrible technology that doesn't even let us know who owns each coin get annihilated. And it was the responsibility of people who put money in there to evaluate beforehand and know that PoS is not deterministic, for example.
About government censoring and wanting to steal money, or criminals using sidechains, I think the argument is very weak because these same things can happen today and may even be happening already: i.e., governments ordering mining pools to not mine such and such transactions from such and such people, or forcing them to reorg to steal money from criminals and whatnot. All this is expected to happen in normal Bitcoin. But both in normal Bitcoin and in Drivechain decentralization fixes that problem by making it so governments cannot catch all miners required to control the chain like that -- and in fact fixing that problem is the only reason we need decentralization.
-
 @ da0b9bc3:4e30a4a9
2025-03-31 06:32:43
@ da0b9bc3:4e30a4a9
2025-03-31 06:32:43Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/929968
-
 @ b4f80629:1ddda3b4
2025-03-31 05:00:00
@ b4f80629:1ddda3b4
2025-03-31 05:00:00def create_basic_html(title, heading, paragraph): """ Creates a simple HTML string.
Args: title: The title of the HTML page. heading: The main heading of the page. paragraph: A paragraph of text for the page.
Returns: A string containing the HTML code. """
html_string = f"""
{title} {heading}
{paragraph}
""" return html_string
Example usage:
my_title = "My First Webpage" my_heading = "Welcome!" my_paragraph = "This is a simple webpage created with Python."
my_html = create_basic_html(my_title, my_heading, my_paragraph)
To save to a file (optional):
with open("my_page.html", "w") as f: f.write(my_html)
print("HTML created! (Check 'my_page.html' in the same folder as this python code)")
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28neuron.vim
I started using this neuron thing to create an update this same zettelkasten, but the existing vim plugin had too many problems, so I forked it and ended up changing almost everything.
Since the upstream repository was somewhat abandoned, most users and people who were trying to contribute upstream migrate to my fork too.
-
 @ b4f80629:1ddda3b4
2025-03-31 04:58:26
@ b4f80629:1ddda3b4
2025-03-31 04:58:26Imagine you have a cool skill, like drawing, writing, or making videos. Freelancing is like using that skill to do small jobs for different people or companies. How it Works: * You're Your Own Boss: You decide when and where you work. * You Choose Your Jobs: You pick projects that you like. * You Get Paid for Your Skills: People pay you for the work you do. Examples: * If you're good at drawing, you could make digital art for someone's social media. * If you like writing, you could help someone write short stories or articles. * If you are good at video editing, you could edit videos for someone. Things to Know: * It takes time and effort to find jobs. * You need to be organized and good at communication. * It is very important to get permission from your parents or guardians before you begin any online money making ventures. Freelancing is a way to use your creativity and skills to earn money. It can be a fun way to explore different interests and build your experience.
-
 @ 6be5cc06:5259daf0
2025-03-31 03:19:46
@ 6be5cc06:5259daf0
2025-03-31 03:19:46Introdução à Sociedade de Condomínios Privados
Uma sociedade não deve ser construída sobre coerção, mas sim sobre associações voluntárias e interações espontâneas entre indivíduos. A sociedade de condomínios privados surge como uma alternativa natural ao modelo atual de centros urbanos, substituindo a imposição centralizada por estruturas baseadas em contratos e livre associação. Cada condomínio é uma unidade autônoma, gerida por aqueles que ali residem, onde os critérios de entrada, as regras internas e o comércio são definidos pelos próprios participantes. Essa estrutura permite que indivíduos se agrupem com base em valores compartilhados, eliminando os conflitos artificiais impostos por estados e legislações homogêneas que não respeitam a diversidade de preferências e estilos de vida.
O objetivo dessa sociedade é simples: permitir que as pessoas vivam de acordo com seus princípios sem interferência externa. Em um mundo onde a coerção estatal distorce incentivos, os condomínios privados oferecem uma alternativa onde a ordem surge do livre mercado e da cooperação voluntária. Os moradores escolhem seus vizinhos, definem suas próprias normas e interagem economicamente conforme suas necessidades e interesses. O modelo elimina a necessidade de um controle central, pois os incentivos derivados do livre mercado levam ao desenvolvimento de comunidades prósperas, onde a reputação e a confiança mútua são mais eficazes do que qualquer imposição estatal. Assim, essa sociedade representa a evolução lógica do conceito de liberdade individual e propriedade privada como pilares fundamentais da ordem social.
Público-Alvo e Identidade
Os condomínios privados refletem o princípio da livre associação, permitindo que indivíduos escolham viver em comunidades alinhadas com seus valores e necessidades sem interferência estatal. Cada condomínio possui uma identidade própria, moldada pelos moradores e seus interesses, criando ambientes onde afinidades culturais, filosóficas ou profissionais são preservadas e incentivadas. Enquanto alguns podem ser voltados para famílias numerosas, oferecendo amplos espaços e infraestrutura adequada, outros podem priorizar solteiros e jovens profissionais, com áreas de coworking e espaços de lazer voltados para networking e socialização. Da mesma forma, comunidades religiosas podem estabelecer seus próprios espaços de culto e eventos, enquanto condomínios para idosos podem ser projetados com acessibilidade e serviços médicos especializados.
Críticos podem afirmar que essa forma de organização resulta em pouca diversidade de habilidades e perspectivas, mas esse argumento ignora a dinâmica das interações humanas e o caráter evolutivo dos intercâmbios entre comunidades. Nenhum condomínio existe isolado; a troca entre diferentes comunidades ocorre naturalmente pelo mercado, incentivando o intercâmbio de conhecimento e serviços entre especialistas de diferentes áreas. Além disso, a ideia de que todos os grupos devem conter uma variedade aleatória de indivíduos desconsidera que a verdadeira diversidade nasce da liberdade de escolha, e não da imposição estatal de convivências forçadas.
Outra crítica possível é que a existência de critérios de entrada pode levar à segregação social. No entanto, essa preocupação deriva da concepção errônea de que todas as comunidades devem ser abertas e incluir qualquer pessoa indiscriminadamente. Porém, a liberdade de associação implica, necessariamente, a liberdade de exclusão. Se um grupo deseja manter determinada identidade cultural, religiosa ou profissional, isso não impede que outros grupos criem suas próprias comunidades conforme seus valores e recursos. Além disso, essa especialização leva a uma concorrência saudável entre condomínios, forçando-os a oferecer melhores condições para atrair moradores. Em vez de uma sociedade homogênea moldada por burocratas, temos um mosaico de comunidades autônomas, onde cada indivíduo pode encontrar ou criar o ambiente que melhor lhe convém.
Autossuficiência e Especialização
A força dos condomínios privados reside na capacidade de seus moradores de contribuírem ativamente para a comunidade, tornando-a funcional e autossuficiente sem a necessidade de intervenções estatais. Diferentes condomínios podem se especializar em áreas específicas ou ter diversos profissionais de diferentes setores, refletindo as competências e interesses de seus residentes. Essa descentralização do conhecimento e da produção permite que cada comunidade desenvolva soluções internas para suas demandas, reduzindo dependências externas e estimulando a prosperidade local.
Os moradores atuam como agentes econômicos, trocando bens e serviços dentro do próprio condomínio e entre diferentes comunidades. Um condomínio voltado para a saúde, por exemplo, pode contar com médicos, enfermeiros e terapeutas que oferecem consultas, aulas e assistência médica particular, remunerados diretamente por seus clientes, sem a intermediação de burocracias. Da mesma forma, um condomínio agrícola pode abrigar agricultores que cultivam alimentos orgânicos, compartilham técnicas de cultivo e comercializam excedentes com outros condomínios, garantindo um fluxo contínuo de suprimentos. Em um condomínio tecnológico, programadores, engenheiros e empreendedores desenvolvem soluções de TI, segurança digital e energia renovável, promovendo a inovação e ampliando as possibilidades de intercâmbio econômico.
A economia interna de cada condomínio se fortalece através de serviços oferecidos pelos próprios moradores. Professores podem ministrar aulas, técnicos podem prestar serviços de manutenção, artesãos podem vender seus produtos diretamente para os vizinhos. O mercado livre e voluntário é o principal regulador dessas interações, garantindo que a especialização surja naturalmente conforme a demanda e a oferta se ajustam. Essa estrutura elimina desperdícios comuns em sistemas centralizados, onde a alocação de recursos se dá por decisões políticas e não pelas necessidades reais da população.
Alguns argumentam que a especialização pode criar bolhas de conhecimento, tornando os condomínios excessivamente dependentes de trocas externas. Contudo, essa preocupação desconsidera a natureza espontânea do mercado, que incentiva a cooperação e o comércio entre comunidades distintas. Nenhum condomínio precisa produzir tudo internamente; ao contrário, a divisão do trabalho e a liberdade de escolha promovem interdependências saudáveis e vantajosas para todos. Assim, cada morador se insere em um ecossistema dinâmico, onde suas habilidades são valorizadas e sua autonomia preservada, sem coerções estatais ou distorções artificiais impostas por planejadores centrais.
Infraestrutura e Sustentabilidade
A solidez de uma sociedade baseada em condomínios privados depende de uma infraestrutura eficiente e sustentável, projetada para reduzir a dependência externa e garantir o máximo de autonomia. Sem um aparato estatal centralizador, cada comunidade deve estruturar seus próprios meios de obtenção de energia, água, alimentação e demais bens essenciais, garantindo que suas operações sejam viáveis a longo prazo. Essa abordagem, longe de ser um entrave, representa a verdadeira inovação descentralizada: um ambiente onde as soluções emergem da necessidade real e da engenhosidade humana, e não de diretrizes burocráticas e regulamentos ineficazes.
Cada condomínio pode investir em tecnologias sustentáveis e autônomas, como energia solar e eólica, reduzindo custos e minimizando a vulnerabilidade às flutuações do mercado energético tradicional. Sistemas de captação e filtragem de água da chuva, bem como a reutilização eficiente dos recursos hídricos, garantem independência em relação a empresas monopolistas e governos que frequentemente administram esse bem de forma ineficaz. Hortas comunitárias e fazendas verticais podem suprir grande parte da demanda alimentar, permitindo que cada condomínio mantenha sua própria reserva de alimentos, aumentando a resiliência contra crises externas e instabilidades de mercado.
Além dos recursos naturais, os espaços compartilhados desempenham um papel fundamental na integração e no fortalecimento dessas comunidades. Bibliotecas, ginásios, creches e salas de aula permitem que o conhecimento e os serviços circulem internamente, criando um ambiente onde a colaboração ocorre de maneira orgânica. A descentralização também se aplica ao uso da tecnologia, plataformas digitais privadas podem ser utilizadas para conectar moradores, facilitar a troca de serviços e produtos, além de coordenar agendamentos e eventos dentro dos condomínios e entre diferentes comunidades.
O Bitcoin surge como uma ferramenta indispensável nesse ecossistema, eliminando a necessidade de bancos estatais ou sistemas financeiros controlados. Ao permitir transações diretas, transparentes e resistentes à censura, o Bitcoin se torna o meio de troca ideal entre os condomínios, garantindo a preservação do valor e possibilitando um comércio ágil e eficiente. Além disso, contratos inteligentes e protocolos descentralizados podem ser integrados para administrar serviços comuns, fortalecer a segurança e reduzir a burocracia, tornando a governança desses condomínios cada vez mais autônoma e imune a intervenções externas.
Alguns podem argumentar que a falta de um aparato estatal para regulamentar a infraestrutura pode resultar em desigualdade no acesso a recursos essenciais, ou que a descentralização completa pode gerar caos e ineficiência. No entanto, essa visão ignora o fato de que a concorrência e a inovação no livre mercado são os maiores motores de desenvolvimento sustentável. Sem monopólios ou subsídios distorcendo a alocação de recursos, a busca por eficiência leva naturalmente à adoção de soluções melhores e mais acessíveis. Condomínios que oferecem infraestrutura de qualidade tendem a atrair mais moradores e investimentos, o que impulsiona a melhoria contínua e a diversificação dos serviços. Em vez de depender de um sistema centralizado falho, as comunidades se tornam responsáveis por sua própria prosperidade, criando uma estrutura sustentável, escalável e adaptável às mudanças do futuro.
Governança e Administração
Em uma sociedade descentralizada, não se deve depender de uma estrutura estatal ou centralizada para regular e tomar decisões em nome dos indivíduos. Cada condomínio, portanto, deve ser gerido de maneira autônoma, com processos claros de tomada de decisão, resolução de conflitos e administração das questões cotidianas. A gestão pode ser organizada por conselhos de moradores, associações ou sistemas de governança direta, conforme as necessidades locais.
Conselhos de Moradores e Processos de Tomada de Decisão
Em muitos casos, a administração interna de um condomínio privado pode ser realizada por um conselho de moradores, composto por representantes eleitos ou indicados pela própria comunidade. A ideia é garantir que as decisões importantes, como planejamento urbano, orçamento, manutenção e serviços, sejam feitas de forma transparente e que os interesses de todos os envolvidos sejam considerados. Isso não significa que a gestão precise ser completamente democrática, mas sim que as decisões devem ser tomadas de forma legítima, transparente e acordadas pela maior parte dos membros.
Em vez de um processo burocrático e centralizado, onde uma liderança impõe suas vontades sobre todos a muitas vezes suas decisões ruins não o afetam diretamente, a gestão de um condomínio privado deve ser orientada pela busca de consenso, onde os próprios gestores sofrerão as consequências de suas más escolhas. O processo de tomada de decisão pode ser dinâmico e direto, com os moradores discutindo e acordando soluções baseadas no mercado e nas necessidades locais, em vez de depender de um sistema impessoal de regulamentação. Além disso, a utilização de tecnologias descentralizadas, como plataformas de blockchain, pode proporcionar maior transparência nas decisões e maior confiança na gestão.
Resolução de Conflitos
A resolução de disputas dentro dos condomínios pode ocorrer de forma voluntária, através de negociação direta ou com o auxílio de mediadores escolhidos pelos próprios moradores por meio de um sistema de reputação. Em alguns casos, podem ser criados mecanismos para resolução de disputas mais formais, com árbitros ou juízes independentes que atuam sem vínculos com o condomínio. Esses árbitros podem ser escolhidos com base em sua experiência ou especialização em áreas como direito, mediação e resolução de conflitos, com uma reputação para zelar. Ao contrário de um sistema judicial centralizado, onde a parte envolvida depende do Estado para resolver disputas, os moradores possuem a autonomia para buscar soluções que atendam aos seus próprios interesses e necessidades. A diversidade de abordagens em um sistema de governança descentralizado cria oportunidades para inovações que atendem diferentes cenários, sem a interferência de burocratas distantes dos próprios problemas que estão "tentando resolver".
Planejamento Urbano e Arquitetura
A questão do design dos condomínios envolve não apenas a estética das construções, mas também a funcionalidade e a sustentabilidade a longo prazo. O planejamento urbano deve refletir as necessidades específicas da comunidade, onde ela decide por si mesma como construir e organizar seu ambiente.
Arquitetos e urbanistas, muitas vezes moradores especializados, serão responsáveis pela concepção de espaços que atendam a esses critérios, criando ambientes agradáveis, com áreas para lazer, trabalho e convivência que atendam às diversas necessidades de cada grupo.
Além disso, condomínios com nessecidades semelhantes poderão adotar ideias que deram certo em outros e certamente também dará no seu.Segurança e Vigilância
Em relação à segurança, cada condomínio pode adotar sistemas de vigilância e proteção que atendam à sua realidade específica. Algumas comunidades podem optar por sistemas de câmeras de segurança, armamento pleno de seus moradores, patrulhamento privado ou até mesmo formas alternativas de garantir a proteção, como vigilância por meio de criptografia e monitoramento descentralizado. A chave para a segurança será a confiança mútua e a colaboração voluntária entre os moradores, que terão a liberdade de definir suas próprias medidas.
Comércio entre Condomínios
A troca de bens e serviços entre as diferentes comunidades é essencial para o funcionamento da rede. Como cada condomínio possui um grau de especialização ou uma mistura de profissionais em diversas áreas, a interdependência entre eles se torna crucial para suprir necessidades e promover a colaboração.
Embora alguns condomínios sejam especializados em áreas como saúde, agricultura ou tecnologia, outros podem ter um perfil mais diversificado, com moradores que atuam em diferentes campos de conhecimento. Por exemplo, um condomínio agrícola pode produzir alimentos orgânicos frescos, enquanto um condomínio de saúde oferece consultas médicas, terapias e cuidados especializados. Já um condomínio tecnológico pode fornecer inovações em software ou equipamentos de energia. Podem haver condomínios universitários que oferecem todo tipo de solução no campo de ensino. Ao mesmo tempo, um condomínio misto, com moradores de diversas áreas, pode oferecer uma variedade de serviços e produtos, tornando-se um centro de intercâmbio de diferentes tipos de expertise.
Essa divisão de trabalho, seja especializada ou diversificada, permite que os condomínios ofereçam o melhor de suas áreas de atuação, ao mesmo tempo em que atendem às demandas de outros. Um condomínio que não se especializa pode, por exemplo, buscar um acordo de troca com um condomínio agrícola para obter alimentos frescos ou com um condomínio tecnológico para adquirir soluções inovadoras.
Embora os condomínios busquem a autossuficiência, alguns recursos essenciais não podem ser produzidos internamente. Itens como minérios para construção, combustíveis ou até mesmo água, em regiões secas, não estão disponíveis em todas as áreas. A natureza não distribui os recursos de maneira uniforme, e a capacidade de produção local pode ser insuficiente para suprir todas as necessidades dos moradores. Isso implica que, para garantir a qualidade de vida e a continuidade das operações, os condomínios precisarão estabelecer relações comerciais e de fornecimento com fontes externas, seja através de mercados, importações ou parcerias com outras comunidades ou fornecedores fora do sistema de condomínios. O comércio intercondomínios e com o exterior será vital para a complementaridade das necessidades, assegurando que os moradores tenham acesso a tudo o que não pode ser produzido localmente.
O sistema econômico entre os condomínios pode ser flexível, permitindo o uso de uma moeda comum (como o Bitcoin) ou até mesmo um sistema de troca direta. Por exemplo, um morador de um condomínio misto pode oferecer serviços de design gráfico em troca de alimentos ou cuidados médicos. Esse tipo de colaboração estimula a produtividade e cria incentivos para que cada condomínio ofereça o melhor de seus recursos e habilidades, garantindo acesso aos bens e serviços necessários.
Relações Externas e Diplomacia
O isolamento excessivo pode limitar o acesso a inovações, avanços culturais e tecnológicos, e até mesmo dificultar o acesso a mercados externos. Por isso, é importante que haja canais de comunicação e métodos de diplomacia para interagir com outras comunidades. Os condomínios podem, por exemplo, estabelecer parcerias com outras regiões, seja para troca de produtos, serviços ou até para inovação. Isso garante que a rede de condomínios não se torne autossuficiente ao ponto de se desconectar do resto do mundo, o que pode resultar em estagnação.
Feiras, mercados intercondomínios e até eventos culturais e educacionais podem ser organizados para promover essas interações. A colaboração entre as comunidades e o exterior não precisa ser baseada em uma troca de dependência, mas sim numa rede de oportunidades que cria benefícios para todas as partes envolvidas. Uma boa reputação atrai novos moradores, pode valorizar propriedades e facilitar parcerias. A diplomacia entre as comunidades também pode ser exercida para resolver disputas ou desafios externos.
A manutenção de boas relações entre condomínios é essencial para garantir uma rede de apoio mútuo eficiente. Essas relações incentivam a troca de bens e serviços, como alimentos, assistência médica ou soluções tecnológicas, além de fortalecer a autossuficiência regional. Ao colaborar em segurança, infraestrutura compartilhada, eventos culturais e até mesmo na resolução de conflitos, os condomínios se tornam mais resilientes e eficientes, reduzindo a dependência externa e melhorando a qualidade de vida dos moradores. A cooperação contínua cria um ambiente mais seguro e harmonioso.
Educação e Desenvolvimento Humano
Cada comunidade pode criar escolas internas com currículos adaptados às especializações de seus moradores. Por exemplo, em um condomínio agrícola, podem ser ensinadas práticas agrícolas sustentáveis, e em um condomínio tecnológico, cursos de programação e inovação. Isso permite que crianças e jovens cresçam em ambientes que reforçam as competências valorizadas pela comunidade.
Além das escolas internas, o conceito de homeschooling pode ser incentivado, permitindo que os pais eduquem seus filhos conforme seus próprios valores e necessidades, com o apoio da comunidade. Esse modelo oferece uma educação mais flexível e personalizada, ao contrário do currículo tradicional oferecido pelo sistema público atual.
Os condomínios universitários também podem surgir, criando ambientes dedicados ao desenvolvimento acadêmico, científico e profissional, onde estudantes vivem e aprendem. Além disso, programas de capacitação contínua são essenciais, com oficinas e cursos oferecidos dentro do condomínio para garantir que os moradores se atualizem com novas tecnologias e práticas.
Para ampliar os horizontes educacionais, os intercâmbios estudantis entre diferentes condomínios podem ser incentivados. Esses intercâmbios não se limitam apenas ao ambiente educacional, mas também se estendem ao aprendizado de práticas de vida e habilidades técnicas. Os jovens de diferentes condomínios podem viajar para outras comunidades para estudar, trabalhar ou simplesmente trocar ideias. Isso pode ocorrer de diversas formas, como programas de curto e longo prazo, através de acordos entre os próprios condomínios, permitindo que os estudantes se conectem com outras comunidades, aprendam sobre diferentes especializações e desenvolvam uma compreensão mais ampla.
Essa abordagem descentralizada permite que cada comunidade desenvolva as competências essenciais sem depender de estruturas limitantes do estado ou sistemas educacionais centralizados. Ao proporcionar liberdade de escolha e personalização, os condomínios criam ambientes propícios ao crescimento humano, alinhados às necessidades e interesses de seus moradores.
A sociedade dos condomínios privados propõe uma estrutura alternativa de convivência onde as pessoas podem viver de acordo com seus próprios valores e necessidades. Esses condomínios oferecem um modelo de organização que desafia a centralização estatal, buscando criar comunidades adaptáveis e inovadoras. A liberdade garante que as habilidades necessárias para o sustento e crescimento das comunidades sejam mantidas ao longo do tempo.
A troca de bens, serviços e conhecimentos entre os condomínios, sem a imposição de forças externas, cria uma rede de boas relações, onde o comércio e a colaboração substituem a intervenção estatal. Em vez de depender de sistemas coercitivos, cada condomínio funciona como um microcosmo autônomo que, juntos, formam um ecossistema dinâmico e próspero. Este modelo propõe que, por meio de trocas voluntárias, possamos construir uma sociedade mais saudável. Lembre-se: Ideias e somente ideias podem iluminar a escuridão.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Flowi.es
At the time I thought Workflowy had the ideal UI for everything. I wanted to implement my custom app maker on it, but ended up doing this: a platform for enhancing Workflowy with extra features:
- An email reminder based on dates input in items
- A website generator, similar to Websites For Trello, also based on Classless Templates
Also, I didn't remember this was also based on CouchDB and had some couchapp functionalities.
-
 @ d5c3d063:4d1159b3
2025-03-31 03:18:05
@ d5c3d063:4d1159b3
2025-03-31 03:18:05ทำไมทุกครั้งที่รัฐแจกเงิน คนถึงเฮ..ดีใจ แต่พอพูดถึงตลาดเสรี กลับโดนมองว่าใจร้าย
แล้วทำไมนักเศรษฐศาสตร์กระแสหลัก ถึงยังไม่อินกับ “ตลาดเสรี” ทั้ง ๆ ที่ทุกคนก็เห็นแล้วว่าแนวคิดของ Keynes และ Marx มันล้มเหลวซ้ำแล้วซ้ำเล่าในทางปฏิบัติ แต่นักเศรษฐศาสตร์ก็ยังเอาทฤษฎีพวกนี้มาใช้อยู่ดี...
ทำไมนะ ?
ก็เพราะแนวคิดพวกนี้มัน “ฟังดูดี” มันให้ “คำตอบ ตำอธิบายที่ถูกใจ” มากกว่า “ความจริง ที่ฟังแล้วไม่เข้าหู”
Keynes ทำให้รัฐบาลดูฉลาดขึ้นเวลาที่ใช้เงินเกินตัว ใครจะกล้าทักละว่า เฮ้ย “รัฐอย่าเพิ่งก่อหนี้นะครับ” ก็เคนส์เค้าบอกว่า “การใช้จ่ายจะช่วยกระตุ้นเศรษฐกิจ” นี่หน่า
ส่วน Marx ก็สอนให้เราฝันกลางวัน ที่คนทุกคนจะต้องเท่าเทียม ไม่มีใครรวยกว่าใคร มันฟังแล้วดูดี เหมือนได้คืนความยุติธรรมให้สังคม แต่ไม่มีใครบอกว่า ราคาของความเท่าเทียมแบบปลอมๆ นั้น ต้องแลกกับ "เสรีภาพ" ที่เรามีนะ
ทีนี้ ลองหันกลับมาดูตลาดเสรี
มันไม่ได้พูดเพราะ (แต่ก็ไม่ได้หยาบคาย) มันไม่ได้สัญญาอะไร (ไม่ต้อง"ขอเวลาอีกไม่นาน") แต่มันซื่อสัตย์ และมันบอกกับเราตรง ๆ ว่า
ถ้าอยากได้อะไรคุณต้องให้ก่อน ไม่มีใครได้อะไรฟรี ๆ และไม่มีใครมีสิทธิขโมยของจากใครไปแม้แต่นิดเดียว
ฟังดูโหดไหม จะว่าโหดก็ได้ แต่มันคือโลกของคนที่ “มีความรับผิดชอบ ในชีวิตของตัวเอง”
คำถามคือ...หรือจริง ๆ แล้ว...เราไม่ได้กลัวระบบ แต่เรากลัวอิสรภาพที่ไม่มีใครมารับผิดแทนเรากันแน่ . . แล้วแบบนี้ “รัฐ” ควรมีหน้าที่อะไรล่ะ ไม่ใช่ว่าเชียร์ตลาดเสรีแล้วต้องเกลียดรัฐไปหมดนะ ตลาดเสรีไม่ใช่โลกของคนไร้กฎหมาย หรือใครอยากทำอะไรก็ได้ตามใจ แต่โลกของตลาดเสรี...ต้องมี “กรรมการ” ที่คอยดูแลเกมให้มันแฟร์
และรัฐในแบบที่ควรเป็นคือ ไม่ใช่คนที่ลงมาเตะบอลแข่งกับนักเตะในสนาม แต่เป็นกรรมการที่คอย “เป่าให้ยุติธรรม” แล้วยืนดูอยู่ข้างสนามอย่างเงียบ ๆ
รัฐที่ดี ไม่ใช่รัฐที่มาแจกเงิน มาอุ้มคนล้ม หรือมาคอยสั่งว่าใครควรได้อะไร แต่เป็นรัฐที่ทำหน้าที่แค่ 3 อย่างง่าย ๆ
-ดูแลไม่ให้ใครมารังแกใคร -ถ้าใครตกลงอะไรกันไว้ ก็ช่วยดูให้มันเป็นธรรม -ไม่เลือกข้าง ไม่เล่นพวก ไม่ใช้อำนาจเพื่อหาเสียง
ก็แค่นั้นพอแล้วจริง ๆ
เพราะทันทีที่รัฐ “อยากเป็นพระเอก” เข้ามาอุ้ม อยากเป็นคนคอยแจก คอยจัดการทุกอย่าง เกมมันก็เริ่มไม่แฟร์…
พอรัฐช่วยคนหนึ่ง ก็ต้องไปหยิบของจากอีกคนมา เหมือนเล่นบอลแล้วกรรมการยิงประตูให้ทีมตัวเอง แล้วสุดท้าย…มันก็กลายเป็นเกม...ที่มีแต่ คนอยาก “อยู่ฝั่งที่ถูกรัฐอุ้ม” (ทุนนิยมพวกพ้อง) ไม่ใช่ทุนนิยมหรือเกมที่เล่นด้วยความสามารถจริง ๆ
รัฐที่ดี ไม่ใช่รัฐที่ “ยิ่งใหญ่ อำนาจล้นฟ้า” แต่คือรัฐที่ให้ผู้คน “ยืนได้ด้วยขาตัวเอง”
แค่นี้เอง...ไม่ต้องมีสูตรซับซ้อน ไม่ต้องมีทฤษฎีเยอะ แค่มีสติ ไม่เอื้อใคร ไม่แทรกแซงเกินจำเป็นก็พอแล้ว
Siamstr
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 6b0a60cf:b952e7d4
2025-04-01 11:53:31
@ 6b0a60cf:b952e7d4
2025-04-01 11:53:31nostr:nevent1qqspynu0th85xlczqgnafy2na46mg276u0c5dmpd9utcz36npmqdmpsunn5rl nostr:nevent1qqs06cvm4qq9ymt2j58u0p7c46j2atxevjkp5vpezvlzesxcp7v03fqm0tp5k nostr:nevent1qqs8vjpu7wd5h7p0elysezzml7wzhaxgjwnp5h7yst0uudyy8pjt3pckcapzl nostr:nevent1qqswmpc5vghej8uz5mk8nta2szx3ejdsvdrvxtspmc3mld683j53mfsf0ujes nostr:nevent1qqs9cwaua4gvrxms3qz8rntj7jmuyvv953sm9lcwk5j4p8jfc4qxpgc7sfhw2 nostr:nevent1qqsx4f2m3njh0cpgqe376xpqde65ujq0aq50nj45ttfqls3yzluqujgpuum60 nostr:nevent1qqsrx7q02xfyak54zcmh233trqtpw725ywasfyg9dz08prxdvcnnuhqdnymnw nostr:nevent1qqsdllaud8mjpfhfzgu9nxjgvys5g08eu344909nyekrrn92pzhpxac56vtuj nostr:nevent1qqsxhx3skvs8xeddpwvhct3yhp02vgmdu90my67ttlj70muhcu3malqjadl5f nostr:nevent1qqs2k5q965ppnvxs7tna9wwx3njtp9r40ur4ahud8ykug85vth03haqe6m4py nostr:nevent1qqspzh3q002ssre56emu2kkhel82sd9j2sacd75fm998km8p6cxn8gg7agpxy nostr:nevent1qqsy8v9vj7u3jfnmhl6867n847d2gs7gpvdn5zdnm98nes9zlgu3rnqjkwmt9 nostr:nevent1qqsq559y4mj940540zhzxa9teknz74l9d6tqptste7l4lqu5yfvu2tg74dky7 nostr:nevent1qqs8gq3t2wk6qluhcjqy5cp8v3y20wmtw3uyfujmga7njpq3fe76pcgtgp34k nostr:nevent1qqsztaj9ut2lxru8la8lcs95lgyrpypwhgx92jc74r5nj7ss8tf9fvsr70m5v nostr:nevent1qqsghxwhmfywe40sdrq2cw750ug5f62nfh2u3jwe476zj6s0xmgcgpchj5qwx nostr:nevent1qqsdaw986p4qwujz99a0eg0yqtpjqhl6rcamxa0hn0yyg8pcwch6cysmans7p nostr:nevent1qqsyh8g0et5catuar388v56eahc4qmf7l6t79cs6scuuqa72vxj5lxq7de8wr nostr:nevent1qqszvxdc8vf2tjlayf7qf839p2j245nt7447ytqnju65s4ypz402gecrcsp8q nostr:nevent1qqspyx8mxme44n9vjspewch8s2tmtezt3z87kpytzetn68m39f0yhfsskl808 nostr:nevent1qqsdu6r2sf6npr3xn5gwkdc6st62zvy6r6r8u7sh078rjd7cjvy5jdcy8crru nostr:nevent1qqsrc0j0xa769ymehgxjem3lchwccndwj3ms922ltu7r7sy567lyzncddqjsv nostr:nevent1qqs0gcr269zzgcmrq6fjyzgqh7lqerhqqaknfrd5k563xnr9vanmtgcfzza5l nostr:nevent1qqsru4vxn5sw02zq4v44xtcpkt0qxqp9yc6gyy5pyavvvwa96dxyzscp3apme nostr:nevent1qqsp0ajlpxnvu64recf69efhxzv6sgu7yk235u59nj2v529dq92x2wgvcna9c nostr:nevent1qqsdmcrqmdkzf9tptgh5mytuan9q3ur7l50a5kjfrskfr54gxqq5k0szyhfsj nostr:nevent1qqsfk0duvuamrutcpansw3hqarnmhcr4vp0zt9r8pta9zlycma2jscs5wz0fm nostr:nevent1qqs82xxv600mtzxhhped2vn9yw7aer487ws8yy5hk5ppyuzxjw92hzs06hxp6 nostr:nevent1qqsfs96nd96mvulw9yp0dyygdtsegxkmnvytkq5xgmepkrh0504x0ns0rnm60 nostr:nevent1qqspa5f2fc5w4f9ghq2eryjnc44hs3grmaq6eyrx4s7ggkpjdmx2gjckswv0a nostr:nevent1qqs96s99kv7h207twu8s9mhmms7e5ck2s9qhndnp0m2w3uqpsh724ysnd6esu nostr:nevent1qqs8z5jzrlmeenpst0xtrm336tt0racrx63cnchskgs2d9cgmrtugdgmluxwa nostr:nevent1qqs9aqladqaf2jvanehny0mhd6mq9cdrgwr838z68p8h9clmcgf0zygqfvdd9 nostr:nevent1qqsd2m5tlpztgfqhzhc09upzzc876j6s60299m9lha2sxvnyjrvfasctaurj9 nostr:nevent1qqsg2yq7mw55vqnjmrfetc453v3z6vzzynmevt2ljgg4yppn5m2ry3ce2jlfe nostr:nevent1qqsr3vckac3re8ayyhv3m3g5s8a4rat5720un7qle8am2lfn7ew3magu6vk8f nostr:nevent1qqsg73fke3mszmuz0nh7r34sl3jlgdx70npfjc5almxrpycykhvnersq3rfaq nostr:nevent1qqsr73gdk6n0dgvg7nv6c390qf0c2j80t7qf99nftmze3dlr7k3nhpsfhl2ql nostr:nevent1qqs2mfw8a5vz3tjrnuerw6vxge0t6kd6snyeaj5jpfye7jvkqyqsv8cdw09np nostr:nevent1qqsr3qpal7xkhkttp4jrmjehm86ulh8hzarusgnyhhuf4ttdkqq0vhg7279w0 nostr:nevent1qqs0m4l3rza008tax28s3mh0tpexeqpzk8y2hlx2h8dgaqcft4rvm5c8xz2sq nostr:nevent1qqszt96jl70h9ku86s8mldsa8vk7m2vtwgfc2sksxcqfmkl2dksjntsjhz5zx nostr:nevent1qqsqdhulqcal3edfn2tu5lsj2tcgyq73zft3z6sa0xaqt4rd7m2gq4qpgs30l nostr:nevent1qqsygu35a9rrlh8ld5nuucjj9nw4up0d8mx6dmq98hqpj7j2kc6w7ts44y0wh nostr:nevent1qqsfnzz55mveegemu9nmqvfvm4wyarpevh29m778946lphw4wya23ms7z8ll2 nostr:nevent1qqs02ft4599adqeu9v3ny04k5x3mdued0rnj2hgg5lsg82xmqnpgxvsr48clp nostr:nevent1qqstkr7gr3flahhe9e6gl70sudqm5qz23rq2f2q9as3ys9s6l9c06lsgrduvd nostr:nevent1qqsqzmjj8rn6pl8wrn5km7an00cfhy5wzqzz9nlne5hzhktwlnsp0ag0qd665 nostr:nevent1qqsfc2x5vx23yyztnvr3n59dv9kyw64jc88pxxfgawt4c8m32qq5ekqqe4neh nostr:nevent1qqs0f7fkwlky42jxsdgr33xttz3rkg7gk200qkmv2rulrlauqwee7ts7mzn5q nostr:nevent1qqsg3c8qyp4n86qdtkyzcnk6kr7gnmad3sd2vhel52m3r64ala9rqugrcnnv6 nostr:nevent1qqsw9dn2cuhe4xu76z2xyugh8gaah92rdyazyg0s2mvkll0qrll02gs4uvvvk nostr:nevent1qqsv0pymkvfqz53jyqwqjj5wypp375ljlstav67zzpdlq536xpm8d6snawjc0 nostr:nevent1qqs20fpumlhmzs49mlsvd2f0s7kfgjq68auzkfvf6s3yr7a0njy782qv778m2 nostr:nevent1qqswqq7pl8g5redm0t82k4ys50w65z03m5xl6ayr374c2vknqfwjcrgguyt5s nostr:nevent1qqsp0fn3adqdq3jvcna0vwkwjnaq32lx6ac7qzpquvdt8zpugx5gvhshhkgez nostr:nevent1qqsvtd6surkas9nrvnlndk3r53aqq82dedmm8ayf2zhrv9w9lf90g8gslhagd nostr:nevent1qqsqw56qfhvkv56ss5r066yrf2hnwchcn4ldav576ldhvk3jk543clcsayyfz nostr:nevent1qqsxq9faxju2wp9zl5gw7usu00rkm7n0x9ylnlujsjjn323wppqpausm4etyu nostr:nevent1qqsrl7gdwgd5mqf3s3ygn2e5j34qnjxeldr99qwn7lge3ncfdwhf4usl70dm2 nostr:nevent1qqsd2a32drg7teet8fnkauxede52lyrau8ey24dzzqflu7pad2fhsvsdgtyr4 nostr:nevent1qqsv5uqj4zxhdtdapzk44tfuxyft55tlp900r4l7rf9vtma8d6cgjms2hjwde nostr:nevent1qqszcepleg57p2k03e06et848frekk79x3f523nmx8t3guxmuyfgsyqeat4pt nostr:nevent1qqsvklay6j4ukvc0w9n74u5hzselsrmclm9jfmezrztqf3xf74522ac0rlcen nostr:nevent1qqs909ldkkvchacs32hpj4zphwxdyxtnvv2nz0wdk7d26ec25j7xyfcsx997r nostr:nevent1qqs0nyvnc4j8xen06z9t784htam8e9jsucpm7g0xq2cdtenxrcx4qdgmgtj8q nostr:nevent1qqsfq3gqv98x97s0wu2cyenz5ng0v52fsv8erzyuj8q7ls9kwaaafggwt30r0 nostr:nevent1qqs2pu4lcqakjgkx524jvd967vk2fkuw6urtp7tw38q3accra6hf0xqd99kc3 nostr:nevent1qqsvgwlfeju2qsnllqgexscdrta9lnqamxlq2kvansadmhyy0g0eqhg02dpeg nostr:nevent1qqsvveq4k9cz0t3xh55cudydkweh58aekjrmqh6zut7ekqsnuv3hfyqdrru6x nostr:nevent1qqsfn29l63mfggnvq2j3ns9u09su2zrsahrxmczh4mk6q8mq45lxkps5alh6e nostr:nevent1qqszg3s0jdwj4qug6plqe865ul8zh6j60gue9c5f897dclmvu5xc2zqv77xmu nostr:nevent1qqswla2n4l5cu2z3czyt8vyawylv2hxj2avjg0lx6lnl7cw9p3kn5ac9nf5u8 nostr:nevent1qqsf8qufcluup4tl8rcngu5z8tarzxl7the3wfe0xnfdyjht9rzvpaqyzcn57 nostr:nevent1qqs8turf9zhsjc7uunw8wgqtd7dc5wtlrgxf2wrvsnw2cgz534wd6sghzcgw4 nostr:nevent1qqsqwngx9nxgf7slse6yeh9uvnpmwz3exa95qyh6x3ez00z72y2jvwsrfqdhk nostr:nevent1qqsv8z7leemtzl5cfexxynl7243uqd4nr7kacdaumyx8rq46kune2psgz47rc nostr:nevent1qqsp0ttn3kcnds34zjew7w7e8hwnaa8hwx29t3tej2guawf8pdt9csgz4m9nv nostr:nevent1qqszy0yufenkexssavnv0p5k98e3vu77f4r4tze5v6p94gmgcrgpx4qd27h77 nostr:nevent1qqs2xj626q46rpzwnas5259t5ywpwzltnvj3pwvrjcqseddtyu500qg5rn883 nostr:nevent1qqsw02jdkpg2vzs5k5c3ymvndsrkje6uwkxf0dqmz0yvycfwt6lvq6qjqgfgz nostr:nevent1qqs2d237yzkmuxl82fc2u7wdpzxyvjw2gje6vgadtw4dzmnp483jgrcval8vd nostr:nevent1qqsrwqj390vqwp7e6nwu3k8m6h4luks86gq3sql99k5tnvy4w52kamqp73nl8 nostr:nevent1qqstdtqpxl78ecn9x8dzylvzul0cfsxh64gfunzts72l3sqmvzt0ylqwp9c8n nostr:nevent1qqswcvajl70frlhwtuch6cwlsehl0u7f2hfw27vhxvzwhzatm2ugjss4zle92 nostr:nevent1qqszfrq6zdsclykmeke3a7znqgp7y975mslf5w0fk0hfujajj9jh4hssc4s7f nostr:nevent1qqsp253cwmp33yedu7asa6k2f09w08j34zcky52ks6jh97msqsrh9nqylwer9 nostr:nevent1qqsd3u0gms7u8gqkvhpfqlvk2jrttjzs5zuvc8qdl3g5pse4dt8ugcsqcez79 nostr:nevent1qqsxq8t0u67schrxvv0dtuf2j6nlvqytkez42f0jmhpjtnkap5ssvsgm7pdcc nostr:nevent1qqsvp878n0zlqkge6famsdwcqp8k92flz2wf97c0emxlsrf7f6gqt8gyzkgp8 nostr:nevent1qqsx3xnxupzzfvws2etneycjyvcx0n7mcqru09gyym5x20s3n9ewcrgcsetd6 nostr:nevent1qqsf666tlstrgssclusaam50nfk0xjs7m849f70fuv5hw9h7tsmqpegaduhy9 nostr:nevent1qqs23eqhwhvah5yjn54m7n5klw4e5efg8s6994pamz5ejcgnsq4d2wss89y7y nostr:nevent1qqs2q84pdl6qvf8h7yu9g6hfvfzj49z28ea5m6k4lpmwvl86tnuedxqkxxajr nostr:nevent1qqsyf0quzl6ttedn7qftse9386uh0pvp8795egxumyvs8sjckm8xgxs2srhmy nostr:nevent1qqsf7n8rqr2wsjpcuczlcee85227rylnv0kanj4mca0hllptyerd8csnyspns nostr:nevent1qqsycgshmjcqsr76tlhuppp23a49zy4e995lj5wnqm8jkz5vmv9l55cjpughr nostr:nevent1qqsp4vwephtxxlv2pjgupymfl6k288qh6gdzsy8qesmu0natsh095tsnfrpnk nostr:nevent1qqs297q9e00dpmj78rdx2qrjg3hva5ye9p7nke8avagn844jxucudwg2mtxgq nostr:nevent1qqs9c08g0fxv3vy7v5c9gsme0jx6fujkv88k3rtnmxjcd89ejpy72hcadrjas nostr:nevent1qqsvmwsetretl7dm42c3g690llwylyn37cunkauepzj3le3qhaytrjsh2ga9h nostr:nevent1qqsgyqu6zjppqek23fgpzlmg7hqfl4knryjvuflx54ypx70m58gt6rs5s9dms nostr:nevent1qqspxcsk7g56qhapmzek243az6zhv9v5hwupnyg4nn352kvc2z0fw7qklkcv7 nostr:nevent1qqsxwe7u49q4yc4ney5kt6gkfep0v9jlx68r5u0uf9upl7u9mcfxpkcqpu7z8 nostr:nevent1qqsrmyeh30f4kfdleq23w9vgcx9jcqgkv3stg9au5m593tlywlca0lgylty6g nostr:nevent1qqsg2v2e7tthtd8m39ctt7yyqw0lqkx23s7e2fqt4s2ymlnn33n5axg7fy4da nostr:nevent1qqsvtgfln33c2nllxt2797xfqttcuy6qtlh8we8q9lv9gn7r5jy4ahsfqpyg7 nostr:nevent1qqsz2al0emnaf5cjtrtdfv9c9t5ey8475yx5kp5442cg0afmlys6dgg29jq4x nostr:nevent1qqsg8lvelaeq9uyv7hzrxgpelckuz5hpf5g3ajyghj8nsk2ycckv63sllv797 nostr:nevent1qqsxhp4g53ltg7qjz2puzvsdwxk54xev46n8jmc2tlg2pdp529ckgfg2329m7 nostr:nevent1qqs82j5zgk3plkk8fugmflertrl8uc6x36elfeet643npvyuxr39tvcrr2u63 nostr:nevent1qqsd4vye657t504chaqf2d5gwgd5946t9tfg6aq0fnkjljnnmkfmadg3ss3uw nostr:nevent1qqsxhr5lanyrce0c6amgvxzd77a26fpap505hl74jztuc5svst8dtrcvtcl4f nostr:nevent1qqsrdap3r0ptlwxgd0dav04y53w04x0jzh22d4sxksuzfpetf6j8zwgtmay55 nostr:nevent1qqsvyqj4lr5g5swahxxjrpmga3569qlmd96xk6f4xwm84gmwu7aqw4c69zqtx nostr:nevent1qqsf9dntcjdmmzsu0s2t7pnlx6ver9usvaz53hvgtjggfgn8da6eydc7l5gc2 nostr:nevent1qqs9njwwgechxesqycm29asghutvq0e2fec2v4jc0gvpsk2dsnujq8c9vnuuq nostr:nevent1qqs9ahfkkycdlkemndn0dc7am5djnp8pwjnu72sng2tg0pk5kq7jv2skfv95c nostr:nevent1qqsflgngaeu8w2xz2lkzly5rvr3rudcvq4yyrn2w724dlr32p2mulpqasv6vj nostr:nevent1qqswg7qfwtdj38kr9xfp7f6gfvaxm5kpuwp22ueqny5pp6da7snl92svggqww nostr:nevent1qqs256vewt769a0q8teqh3n5eggjvw0jddl4xzejx4rykhcrrx2k4zcr70g2w nostr:nevent1qqstf7w5lej9qqm63x2r9c5ztc7s9tre65f3e27p5mhqjzy3555856g0lptxq nostr:nevent1qqsfzchhw84ldh2egvqethzychr8jvaaurdacvav3qhgelwzldy7adslwelmw nostr:nevent1qqsqy4uzgsedu94j6jyjpavrmn35khc7nsdmhxnwqehy9umdkgac79skwad40 nostr:nevent1qqsrzxkswpug72gc6eqf4qklemc29quyscds2ftwuqmf0lwvz78fckqxq9r9d nostr:nevent1qqsfzvl36d5k89q0frn9gfepwjrd65cgarh3gtj6gmqffjh9v7ncpesfxuyug nostr:nevent1qqs9vcndnjwtjcg2p5yj2jcktscn8lyf766kqtjef2a3fmyhsga0mgg6d5vp7 nostr:nevent1qqsdf65dzcvx2pkwh297amygfcdypu80g3hc2w0hzl6l8ed8ptcd83ccux9kt nostr:nevent1qqsr69tp6y6dj6agued5vqvv8wrhwngtl9nk6yln2amzg4j0fnxfsksj59765 nostr:nevent1qqs0jjfn0tnjgvech67ks5n3x9zrpredskg67twea7m2x8hvuq3zvvsjdgjcx nostr:nevent1qqs8s9wuwnqmkdjwmrxmqrjyktq3egkxlaqzx7t6q9e53yalga55xuq5ez8ug nostr:nevent1qqste2hugs0txe9xqzle5y60t2m5sakxfcq4flw9e6gtxvdlpuy2qqq3ksyc5 nostr:nevent1qqsxrns3rez8vhnym5qvqkg434w26r2paw8jm9640lzmhzs7jc00r2sk5nqq7 nostr:nevent1qqs05du8xmstnuajfj6cqetxv06xk8xgj23eepfpyjk8hdz3v5hx3hqg7tcwf nostr:nevent1qqswq92249238q2gp6cjcuup5w0e60htyqrp22cepc6uelysmewp46s3n3c76 nostr:nevent1qqspwxsck6zz60gc8tr48l4qqdnlnva0s9gay2hmdckutrz5sk8mnpcueftjt nostr:nevent1qqsywqjwwnuycnzkar8cnua5lerl80kr9wvwdr4yy07k2r7enlup08s0w3tg6 nostr:nevent1qqs87m5zz4x2cctfvxrvxx9546fe9rl5j82dxcrz4s89qzk47huyalgrd3rk7 nostr:nevent1qqst7lun76xhcmaw84s7cwqu9wu5dfterxxhjptlw54gxhnz5duxcaceaky47 nostr:nevent1qqsyexk849hlfxhnqlt4t6y23jshgeevrvtu53dh95w6xfeuuxrvz7c2aj87m nostr:nevent1qqsglmpnfw3jgl9ekwanzlgzhndce6pmncvunkswpc3y2n40vu33m0cwds2v5 nostr:nevent1qqsdaw8rm6yww2ks8300m2xw22c8xdemnkspdvwrjh2jn6hnuvuh9zc6quvml nostr:nevent1qqs0p6d8ny8kunevc8capqu9ntjmd9ze24ql2sjam0j0h8ju0xjydygkm9ffq nostr:nevent1qqswu057ppwc2lars6nu8sc8j4rupnahsrn79a8zktsqawq6p5fh46s5t4yqn nostr:nevent1qqs270vsqqtjwjyswfmqyldjnmnvrrp5g5q7wh3k5qj8cuhljwn0j5c8md0u6 nostr:nevent1qqs2ypcx6p5cqe8dqqmrm36qvgucflgvss885r8czcal6zv0axqdr7sn0x2df nostr:nevent1qqsqvf477f73gm2qfkuly89sy4sadju6wh4t6dcqgh4zwr8ds9g9txg9gppkp nostr:nevent1qqswnmvwph8x9xnqr4n6ytxnfz8nl89a7hfrk2453ldxudtql3j4yns2fj3hs nostr:nevent1qqs2ecqgkcgmlvzj90c8trmw3nld0trtuujnv28f5ezt3huhvvtegmcagpf0y nostr:nevent1qqs9s9zkznyxu6qk7svajntw0v02ldr8462dgt7n5f9slq7aleycsusl96zph nostr:nevent1qqsp7nux9qjzsx4ypcrjexrz25clr9586ar5n5ahc70r7yhakzvaeasd63ulx nostr:nevent1qqsp5gp2xg8lx4kneqrhv990x0velm85s5u2jmggkwwzt8yrxygdc8qgfsp3z nostr:nevent1qqsxdt30myarjhkprzt8xx4kfy7fhyjxshaza0z52nq0pkgwkqguhugt0jswa nostr:nevent1qqs2qq3wpva3lt07xrde3y2vehqy0cwyzye52cvhjnlyw5x3rghsgrq93jycs nostr:nevent1qqsw0959762aa5pxz9hhaa6saszqrnqjrr5umtl5kkj00prqka4fc5qnpfek9 nostr:nevent1qqsx5htpawdvx500074r0skyxhrezkfs7rctuu4afp4puykuvth9kksr9dc64 nostr:nevent1qqsf7kexs3s0g0f4dzv9c8qdns6jh6e26qvecu59d579ud0fta8a7ag7pss04 nostr:nevent1qqszkphl8n8vtgfnrpkudwe8nsm47pm95ajy9a7cdaz3k7shadjynaccpqzv6 nostr:nevent1qqsgrperqd4nrjegephrrdcj0qwkk22glfeq3msumte2evup3f5f29cv9e5vq nostr:nevent1qqsqueyp46tjgh4s6fc7af8r6nnpdetrutmemalfkk0ruqp93zt4ltc3hdj29 nostr:nevent1qqsd34zcm5gm0aws879q9t7sdm7r7rvd75sj4uzxxslwa25ffay3pnc4x9wmg nostr:nevent1qqsz233vcgpjrtkn03kh2wv93jwt0m042jpqp06uank9vfummhdrqxgvq0hnj nostr:nevent1qqsxdtchwzjvxvml4h27ta75542vgc6zpdtzeuma4hrz55v9trswdns9dpxna nostr:nevent1qqs922qlylqjrmr3uaj0f29s82smytg67cxcl208memnktx4h7fhhxqd2wzwc nostr:nevent1qqsrpzxupddee90chcj8psnlhhd8s2r68tvz5u09u7u46wj5a0hyyvs98d2z7 nostr:nevent1qqsfkl9ukp2gss96ut95rwyg3gfcdft4qnkzjc6mg2x4dnpxsezwx3g7dl4fg nostr:nevent1qqs03mv7zygd5stzm6mlh3v57mszuhvnumwfpa94m2axlwqhrtyjfacm9hfaj nostr:nevent1qqsg0k2f4l79804jydkq3ryekkjk95rcysswg02ktrg3cftwq5jnvdc6pcn0x nostr:nevent1qqsw8fnh3x09dj7m4w0engzftejh5pq0dgjzcr23erpg38kyvgz6taq9hg083 nostr:nevent1qqsycaw0y5z5te9r8m3sx8cngczuc0dtzcltf6khwgwhls4y3vxv7wcehkkgx nostr:nevent1qqswpdv0jy9ag757st0c29efprl6jttz3jvrgaxg382txm4r38shhcgfnzhvu nostr:nevent1qqswzt4yac0p8536j4venvexgt03shq94xnsp7lmxuy0vq9wl9dj69qqtr6tg nostr:nevent1qqsw5p0cm9wxvwjlv3z2kewze2t4lw073h7x5lql0g3az7h7jnd0pagxxsmwp nostr:nevent1qqsz92z4pa6zdhhchrygypy39x3j8u4mv98dflxmsw39dyuerfgy2xsp7rg2g nostr:nevent1qqsqur6s28xh68lzft7k6suklrv5knjp4hysunyr7g79caucc8vt7yq6kl0zd nostr:nevent1qqsf02sunq6yqjcpjlm8a4ku8txkyte68gmtvmhyez0lx424cxk65zsv6gk3q nostr:nevent1qqspexe5ew6dt7g3ps9tk2cd345y3jd0asfuyj8pgxv4m5ywqw990lqyhzv9m nostr:nevent1qqsyedkwvv6u4ludqgz623ftuj4mncn5c3tzf533q6xgc4k5xgn435s62yr3l nostr:nevent1qqs0qr3al6we2zeqr4lrkz6nk9cp7cvf9ymt06khw7d4377k7ar5n2gxtem3f nostr:nevent1qqsg5x0qrjk38xpmxh83n2wspg32gwwr4hxqjsc6xz60wess9efy4eg6cpn6v nostr:nevent1qqs9swl3twdd9zjr55gsq43gctczv4cjn0an58gn83wf3ujquu0l7lcff4ma9 nostr:nevent1qqsv9sc8m3e36a253p4jg5am9ay92ncjnx9nttsh5ss37ndr4znu97g0lg0hz nostr:nevent1qqs90fava6xzrjhdpkwld3utw3xl6ghddfmlu9ceql8p82mkv6luvwswptxe2 nostr:nevent1qqsrx0h5jz7vjv7ul0w30rjqzg0eey8r0ff0k9cf8jfcjjr5a57kg8s8tz2qy nostr:nevent1qqsfwln27aduh4yw80cqwml5f7vh5z6v7q80gxmrv3a97x8zfw0a7us40qsmx nostr:nevent1qqsyyl03g27p9ekau4v483800dwc02sfeay8txxn67mr3h3zt476sdqv7dc0g nostr:nevent1qqsgup96lkscndr7jdze308kt495s65uura9vjl8yucfcd0depzpe8cdvlxjr nostr:nevent1qqs0c0zwxpfv4krj0vfku448tl3jpudw56nw4wr4whlje7cexauhd0g6zqjxn nostr:nevent1qqs0dvc82lc2mmzvkmqtcua7kt0vwz4am48kj9sq0rk8xpsxjxw5pgg4qe329 nostr:nevent1qqsxzttj97g67mag82fww0aglmvt5qwvk59e7euswn3nmjtpx5j6thg6c3nz7 nostr:nevent1qqs0gxfve8yz6m93jaseldl8xzhsmpt7k3gkqlv8xlje4q6aqjnna0gezcl83 nostr:nevent1qqspj6puxtaj06z2shd9nr82t2rwwmh6mszapee4gjyj7vra6pwfj4q22x99e nostr:nevent1qqspcrj2zg0jyy7ardz4kt4d5n95wz84jl65hmrdxum7nneeglwtnzcxxzdt7 nostr:nevent1qqsd4ddx493uj3wuxscwfjl9le3f7t2f78yh385666knu26vr9luz4gwa0w24 nostr:nevent1qqsx4w8ztgk5m3wz59mm0sqr7nyzx9hzu005vae6kqaepnpxqw0svwqaq9le0 nostr:nevent1qqsztgtzz4nqf8znh8u3q5fwtnx84mzrjur8gq6dmg3mj2kn3ugx2xca4g2nv nostr:nevent1qqsv6m42nk6uerh02wnflytfvj4nuj0sp43s9lzuvd5thprz9k7jjgqgywnf9 nostr:nevent1qqsvennjay5vvk40t99jwnuefa4lw6zuhya4mg74fsd0klrwyfwjjus0atnfx nostr:nevent1qqs8awph7hzu76df5w8k4xx6j5wmc8tnddxa4sfwnuruea78wr4tg8c47rsa3 nostr:nevent1qqst2222z58smd36lltudxlme8fpyupg8t2c34z803n668t5pmt0ypgsv3ryg nostr:nevent1qqsvjphy6fz8ae244jzdha9xxmz2jcy0pz6zfcse626t9ms5xlcyeecmpdyt6 nostr:nevent1qqs93ghgzxt4ywr404yn4jm5lx8m7l964mmgqtl55khza7jfwsk3klcyup39u nostr:nevent1qqsq0lhuuwewq2kgtjk44z8wnuhv9x0lrvym08dk5p70zk3l9gupp3sv3dlrp nostr:nevent1qqsyq8u0tnangar2w7ft0cfzwglxmwk7kkczpj8k7wqjnasz3sq2sgqssvy50 nostr:nevent1qqsyh3f6lhft7mxmf57v68ypfa4j5fdkuvf43c9q0g5w83jtzwsg86gwhjqtp nostr:nevent1qqsysgrlqjk2wayzw0dymw0r0wv30lk0c5qeagc8h7lmulyffj75clg4t4anr nostr:nevent1qqswcpe2hfr6zk46p0jv65kl3wtp63smv6uxe6j4evsav9dlcpe7xmcx9kqrq nostr:nevent1qqsxv5tuzmfjm3dcz05xng5e9gl6e7vqx84h37p83d6qstzx3hwqwlqtw59hv nostr:nevent1qqs86k2c9akxtzvw7upchwu4pnesj4ds3d3fsg8m76mjdpvj38zwcac6vud53 nostr:nevent1qqszltfvvs22flkqd2v9jzuu222nq9jud78z5sjk8z6y7jmqnd3f3fgme3yek nostr:nevent1qqsrglucq53e84kgkaa2hsq6a5xahraethlykzx6znymtg4gvxenkssx4un3a nostr:nevent1qqsvaq0lwefwnrfkvmrul84fneecua2g7eg8henlkuht0r8u0sp79cqqwt7s8 nostr:nevent1qqsfrah0av2l3dc7valuqklryz2a687t7cenharuq7r6xelm0e0yv4s494vpz nostr:nevent1qqsrt7uykaetqwl2q90x6kd5xhgh6apn8kz7gvy6hgsa42xe6qmqgxcmyll46 nostr:nevent1qqsgl80erg8t5cqdz3wnxzd2g6ekhdtm7rt3nxszzvzxft7v7x8lqgc084p04 nostr:nevent1qqs8gsthklfdzy6fku378tf6807qk86kjcgrgaavrjtdffh2e57la8cwltl53 nostr:nevent1qqswjgler7slw0lncaxhtne5kz3np3tu5umdef2aqavy5atq0tvgm9gns8h40 nostr:nevent1qqsr2ka8n6zv0z4mk6ty9nztqd9qz8rkgt6cjck4ce6mtpm8sxupmsqj7s257 nostr:nevent1qqsrudy60t40q9vup3p0kxrrnlllwnwnyh8kt4x623d3f74jctpnrvsmd8zam nostr:nevent1qqsqskyce40lmwc9v94tkxy5phnzf4p55q090g02wt0x40czw8mkk4svtu7a2 nostr:nevent1qqs24dsj4x02x80lvgtj3khkcqpqv6qyypfse2676et46phrztxs75shwde3x nostr:nevent1qqs2cyspyllevj6ahmzep5jhlnnfc8448uh3jn5m2qfmn8y3dma2qggcrtvve nostr:nevent1qqs0k044ntscwad95k8347wuflpchrl0aszzltfyp2nxpv3g6kr2cass8k459 nostr:nevent1qqsqq9cce7umtkm9e3588n7nl4y3dktlskssapph5z6004hqg9setaq4zcqr3 nostr:nevent1qqsdsxzfqhwxg42a652t4234z7p703lwrulfnz9drsus8erjvnag74c3606pt nostr:nevent1qqs0wjxh4ze8xfk7sec3zu4cepwtwexqty80qpvp5nxxgvutk9lqydch9jzp4 nostr:nevent1qqsgavz69cxs6mx2y42j4qnqn7q5xdwvmnaae2tj2px8zdep0j8rs6g87hl3t nostr:nevent1qqsru6z84jtjmycunulyzf5ns3rq0dweseseyq5rxmuzvcs7ylenu9sykk9re nostr:nevent1qqs2kxhn4sl0p8wyxzcv4gpqqwztky37p2j22qhpjqgn0cy407yn03qmsctfx nostr:nevent1qqsf7ug82cd5c02jkm7uahc4p7kc8j32q2dgvuun46ywmlfmrwu6xns3r0egn nostr:nevent1qqszckunp53566u6grgw75gy2c9ce6902zd3jp9cfg20paq66lxxdjs9l259l nostr:nevent1qqs07qw0kashdjyxgj6w92p44hnd3l9jeamxhc63fkdz9cr8na85pwgqlset5 nostr:nevent1qqsga4g5haatk09u4vkm6nfmw6ngctg6p5jzam5kax27lcnc74vcsdc5fwjjf nostr:nevent1qqs8uu57ukvxfvve900uvynudvazpu8xuw7zvexkctm62rdgtpu600qcdwg0y nostr:nevent1qqsgdc297tvnh06kqrg3e68ftyu6prwjqtvxj782f549jugart2jc5gqcqjyp nostr:nevent1qqsqkus0qg7nnl5jkjzhugjpd6vfn70m0r7xtpyz3mhq9k49unuwg6shprvut nostr:nevent1qqsgxaedjvy4s3rlfg8235c7yh0uxc0e7n967p9j6uuz90tzvafzy6qrmcrwe nostr:nevent1qqsv2j2dchuyajecmrqxv9pra3cju03fwkes5qy3xrjtf55twjmx64cjvx347 nostr:nevent1qqsqmnnasdsf5zmqlq3alycl5r2uestvx5mshvnl56fdjk0qx4t2hkgnzn7ww nostr:nevent1qqsvdm79znu685uehrmmegcmq836jj3qeqtym8cv356wx8y5tscjg9c0dvw4y nostr:nevent1qqsy8wx4ujy7z3e6svmz72zaapu7xqx7y4xsuthuk6ynwkzfl9u92nsl42f8c nostr:nevent1qqswccl50t2p57wdfam07p2lvdqzxeg6dzm72vrjsf0xjl88uk03m4gzx25jj nostr:nevent1qqstv4gslzxfte85yckx07fdn5phluvcnj7a7pf28j7hgthkngs7fgqhl5fay nostr:nevent1qqspeada7h3749ex026n4gp60pkv7rtt5nzn4p76dyz9vfzyhxp5puqw6uech nostr:nevent1qqs88tlgk2gd2dsf3mre36e5nurg8afmynkafwlj59p5295wq2dycccjtp7l7 nostr:nevent1qqstu5z907epgq3rechx0ezqyge3uj7nm2j2ty93hj9rwuxxzrljffc4zr0qc nostr:nevent1qqs2r67wggz466rv4kh3vrhyl8e4t26a5s4tq7wgfrglghnhcw47n6q9mhltw nostr:nevent1qqszerzkulum87k7ykzzg0t7wa2lww8ttt7xlu6m385hl5p07lsk9ych3s90p nostr:nevent1qqs804wfmxcdt6gev9qmyasz7mxq6m8k287ulsfz39umqcgpqqf2jnca7xk42 nostr:nevent1qqsgusg06zl58x44778cskde5n8uudgwwajfdq28nvq38kt8nwsyu8qyw6hhx nostr:nevent1qqsy8ecclr3p6s9r7d0ge060fsc6qveuj8509nkndq9stzp4aslejuqw9j892 nostr:nevent1qqsyxns5ze0qm54f3nhpc0dygqnq60e2nmmgpvlhkg99zt2fp7umedc7latuk nostr:nevent1qqs27g6c4vaqxkc2gvnvuged60095fwdsk4e4ze77ylazg9lgz0mlng67q65m nostr:nevent1qqswcy0v5pn5v9wx6uzln6nr4nl4w5d0c688gx5z3qhepswmhu4zgdcrvux38 nostr:nevent1qqst3l22tc9thmnks3nxa9lqdtejktk44ved3xkyqy34dzuzcz92npcdvgtlr nostr:nevent1qqs0jnryazxjjl8g3hxw2xh4fastfy9cu47lpm2qgh2fc6tf4d78sqcphuvzg nostr:nevent1qqsva8k2qn9pjm4wpg879k37f9hxtrpa6twa4ck9uf33e4udzq308rsavs72j nostr:nevent1qqsggahcy8q0zgyvjdpxpljykjahjsx4tkg7z8qr6m28y0hjvfkredsyu0tfj nostr:nevent1qqspayr6m5dcevp96sgew5zn7dye0gm2lrvwmlhr0nlv8kcayarlp9qlntm3p nostr:nevent1qqsdssqj635ee355wdugls0lr7hgfwjjxdzr3appz2pc0wrsp228wrghtxuzg nostr:nevent1qqs0end22ejwqry63pt4yq99ez2jsxj2d35kpy3dfnkmsdx8pk53pjcw2qdwy nostr:nevent1qqsw5t6gr0svp9wefrve6przj6hqlkp7ma787ac8tauxwtc53ws2a8sru5vm9 nostr:nevent1qqsr53vq37g7mm6chgsafpgn9hscgaku6m00mu96d05lryqx285k0yq7ujhye nostr:nevent1qqs8w3ds968pe2jeazwt3ra5y6r3dlgxqgt0an7fd0zy7wm2lkgc2ucahcjqq nostr:nevent1qqs26szux5exxukg7ht579uytrcs72j2j9h2xf4dwvz044jpntsynagqv9sdz nostr:nevent1qqsrej9r6kazt3eda4hhu70tkax4j5ft9l3ve4apnh5u8p9ltj6allgmn68a7 nostr:nevent1qqsq64h92pdffc50xvmlwdfyms802x029qf5pe8fwlu9n4v4rg93t8gfa7kee nostr:nevent1qqs8hhmaww599xz682l2hx0uvn4sfluc6aa7lydk4nugxejqjeaqeugyg0glt nostr:nevent1qqs832edsy9yxhq765zfummutc0r54zc4xj7n9lcuwcf60c66q494zc7tlqgx nostr:nevent1qqs8etkcd8f2aw2s7efjdsj8w5ch8r8ej9capyx976w343ps9sm7s4g0l37gr nostr:nevent1qqsfwaetdhzn3z6fqs50usmktug5v4stcet3lus70p5hffjq8kcpuhqpu5ef4 nostr:nevent1qqswnvtzachtgqc9gwqvcu4s0mtmwxnl78v544p22u6cuud95s2jgmgaz5glx nostr:nevent1qqspmckx784xjj7mkn70tu6rfnyq0kmpcg4p8jr6dmlh98um8dcqnvgj8n426 nostr:nevent1qqsdxeatzq42tstmculgf62rhj84mpgfzsa54gjsh4hrl6e64jv3wfcvr8fec nostr:nevent1qqspcksa07zqnc0xf9h57mpvna4ke5fd5g8lw0v6wycf980lhh9fzes3k5t94 nostr:nevent1qqsy8kvy6s5spzhyfjvj6lzesj0ynnp5d30pqzuwe93d2t3xmrl77dcjz5sfg nostr:nevent1qqsyh342up3pkjfkvzr0yjaxtu4qg5syquz93xyd6fgatdwqxy8e7mgklaf0f nostr:nevent1qqsyp94g3puhpz0k9vaft8tvpqew024n3asxpklgnax6fdsu2mu4kcqkq7fqz nostr:nevent1qqsznp4zqx06tjmplxdr0q548f3kcn7pj4hvf4g4rgm74yk62c59lnswzsdn4 nostr:nevent1qqs29ffntcwt0t5zv7ecrzjgpd6v2r0nqwg9ymm5luhehgrzhlr4f4shqhwee nostr:nevent1qqsfrn6h3hjk4zrs6pamcdzapap0gvemrm2akxlur005chgh4vaps9sx4y5sl nostr:nevent1qqsql32xdfshaa73ex68fz8e4r6e0lhpcgsgdhczwfsq6e7lqqt703cuhue8l nostr:nevent1qqs952dv2ycq0a2tdvyj7st7sd87pxzh7hceth96hhhwjq7gs95m5ccdf764h nostr:nevent1qqs29kzdduhtv7v2gr40nhzkykls6pwmn9maspl2qs83gqkk23ql42cmxwq3n nostr:nevent1qqspwpz06fysr7xqyjfxg296e5d7hcycp3wkmladpe39tkwtmyyaprgycny5j nostr:nevent1qqswsj30jgpyt623gqpy5gk434xeff94cwqrpzpm2tdznhqlvs6dghcuxdx4l nostr:nevent1qqsvty7umlq35gydcj4n2tmzv334yuf5dnw9p662q22rzfq5yhwpk4gz7fnyp nostr:nevent1qqsppkpezwkyfezakg9se8uzvx8j6z33e7k3f4xrpad378m5jua5z4cms7k8m nostr:nevent1qqsykvscexq75xect594xvyp0yzlstagqa62kmpwr94wl7q0exg8h9cwfxcmz nostr:nevent1qqstfqwlc8rmrqrhdt7zdd082eehssdt4r66h3j3ns42cxvnzjegfrc7qr8wd nostr:nevent1qqs0prhhhyvtz3fwwsu93ndvc6ye32zp885eyg6rkxldc37f0jck2eqe3kqr2 nostr:nevent1qqsvr4nsccw9dehyettdc0tr4t3yycvldjxka6cte8uth5r6xz8vhxcat20d4 nostr:nevent1qqsfkxvh4h3ga60l3w3x5ngu777up09sxrqdjgkrnv3yzdhdn2ljsnsylcsge nostr:nevent1qqsfc83pkdtd4jph9r4hjyc4xqczdcem3ytkvp732zalqkl8jhxaq6c26cp54 nostr:nevent1qqszd2hpl8h2uljcgqe0r4zqrk9v0us4nwu5x03v02cx52hkgrlykjqehsv2d nostr:nevent1qqsdz3m0pc789hk8vv7ldhwnz2ydj93qatn5t6g995y9nqkylcfh8hsex7w94 nostr:nevent1qqsvpr85pg2gammm3fqzhw8lme342mplaau3zeeku0up372eps75cfssvpzkt nostr:nevent1qqsq8j9f0vg5an20rdxfpgylaslpf6nt33srglu9f2pthesfqhjgy4s8w3qmn nostr:nevent1qqsyxu3dg4fprxjc4rneslkgucnwx5h4sc7zvd0w0yydkv2hzymletcksa04g nostr:nevent1qqs08n09gvne3d46y8dhxhv68duzvlkwmg9mnv7467cz4x5utgu3rmc0dcuny nostr:nevent1qqs8tcakcm8dqnzef535ylh8j7m5n98s5qu2zydj9w8d2kfa5mgsv2ccpxcqw nostr:nevent1qqs2sm3kfej6t258k6su7krggu362slve3m9gayjyskgvwt0m49ahdsgdmjnm nostr:nevent1qqs8dvmywjutfgx5cw3r9h355dmfufsxwse495svdx79kq820g2u9fgap3umm nostr:nevent1qqsdqram3x44q994z4e93ufqqav5dwa2la28j4fmwqr5swympy5k8esk2py04 nostr:nevent1qqst0vhcp4sy6h7h6c3cfe957z9pj48ujvhw7yhmgjjmqe0d4u5x3hq45hqan nostr:nevent1qqs28z599avfsddedq8dwulzhyhqggs9wukc6jqdp60fp0kcruck7gg048zc5 nostr:nevent1qqsptwc7rfkt7lhkvwz0h2hrrwxj9v0kak9dqg0lph3pfsxq4mna8ac38gqdm nostr:nevent1qqs04rh8vcey9p78kjugs9xvlmyl5m6043n6turhg0d6xrnn745y5fcqkes8f nostr:nevent1qqs0j9h04kfesvcqeax0ynawe7g7j62jhdanmzp0eal57ayqhgn67qqvs8d6h nostr:nevent1qqsrg4gvrwhvj3np8hqyyl6nsz4twjnxdy3wtd99try3t5pkz07e3pc3sn26m nostr:nevent1qqsga3tc0kc02g726fwrwrjm2e5x7tl3vzmv80sd2as9ywht58gcztcgfcrad nostr:nevent1qqsr5srauwprlzlfl0gxnfkaya0rlqwusqnrnkjzmta03kqxx2xc25s5ctflc nostr:nevent1qqs0fjpmu9w0dgc4a808vvals2j23ny6lrp0u0dz89w5mn9749xsalqva29uj nostr:nevent1qqstrrhjlp5h0qetmyll3dzg95yj4rr0m7rzfvp4f0yla2f3g5uj7hcdkkep0 nostr:nevent1qqs9p5z3djta5r223lpdvjgrcc9y9vcm4lsvj69zqfuhrgw3zqeapccfk9dcw nostr:nevent1qqsfrz8sp6sk0u75zwfskwxqgk2t495ymf5fqtalwdptagrx85d0yhsnejvgv nostr:nevent1qqs9a6ujeew8mzmuh8tewk89cv53fahgwyl552hq2qd5zjp5dccc3uq34j4s4 nostr:nevent1qqs8rhur5klw8pfu32nrqh0cp8n6fwgppvpjzpf9q437csc48x5gmmsngq8hr nostr:nevent1qqspr3sgff05240mlyg9y0j7x45qck8x7edzfeqrdafc9l3jwl490wsm4ll68 nostr:nevent1qqs2vzfrp2082gm88uc34zh7pe5zqypgsxkhed4f2aluep2265955vsatghhe nostr:nevent1qqsfjfaz8932tlxz9gqppvmvk9jpqclp6ejg6cdk488xexp5l8jn44gslrmke nostr:nevent1qqs06kyqpy4y6p24p8rpjc728hzn5cu5yvg57nl393t3hzhs4zrhmdgx7s02z nostr:nevent1qqsw5ez3ew4jmeuvz5tg2whsggqfn4097du4jspawxpun375njduxxq4s79hy nostr:nevent1qqsxrrmedupcnyjkv9azw656c0h70x7allk6kv3wqcqq2enar97xc0qmfsdgd nostr:nevent1qqsf88gx3w544ukdxz6wsr70vnhx42ruf7mn6p93e57jqpff4ty3adcgsu5sq nostr:nevent1qqsg7tef7jx07yp4udwnr3mhk4zc9ckdymqsre2xcjcu8y3ejszk0yqes906u nostr:nevent1qqswmqh45286p5uw83kcy38e0qz65xycn06xlwwg48g99kn6mkmmh4sn4nudp nostr:nevent1qqsdgdmdrnk6mf4rcfnqanjtptkazlkry3dnv5wt49znt4xn2ycyvvq2hp8ke nostr:nevent1qqswyueph6kfgwacrdhttat5pnk732m7qcsqt59sptu3cux9hzjw3scte3kfv nostr:nevent1qqs9gw4n83hgclvurawkhpqwtfdqm257kgkzve9gf6gx6n8p0k46acclzglst nostr:nevent1qqsvf9heuqcsxw05uhmnu67884h73mhq27rcv46lhdjhvly9e5eq4lgsalqhu nostr:nevent1qqs0s3mu4k6wey5zjj7rrff26q7nxpt8r2d3qex5mww00dpfqdltpvq56r5nj nostr:nevent1qqsty4e39zsmsax4m5m06wmw3fe05tlkqujk05k9d0sdz053zguagtstnfgu0 nostr:nevent1qqs9rz3at95dava3wnp05wdp7f6s7kl0rzfzpmm04ahk7a38akspzdqw7slkq nostr:nevent1qqs0vwqx7edy8z7m6sr4tjqjscgqf2fmqynkqequq6cp2cw98te5ags908vau nostr:nevent1qqspf7ms32mqyzt46jss7e2eurk66p2j0kdjt4mxx840e4fnfmd0fpgpnanv3 nostr:nevent1qqsfjtqrw4wmzc926gzkmval7s99p0m36vkkag206y25r0yevaw5dqcvk53zu nostr:nevent1qqsdhhmptxgvjxv30r3zkg48kjangs9u9yyfncjs7j26y3xq04r0e6sgktj68 nostr:nevent1qqszzmmc2krvwn6auf9nvhr9uwau66kymjajwzlfukq7evfyee4ukecs0kgyy nostr:nevent1qqst6w7u8lhjzat6vdl5ys7m4dpr2dp07kqrw6qzflehkd2chhu3u6qlwvdha nostr:nevent1qqsgl48cu28690ns7endh3es2ydjv5wjeexv5gqhjmhmgj2alp352tgdzzss3 nostr:nevent1qqs2dzyjlj99mhxznnuvhlqrn9rma6ydatj63umwaxw7yzvlltafyqcv3f9mz nostr:nevent1qqsgu088v434nqvnnqrsltnuvhh68698gm5acgmne3k67lh48au8vtc6ys0jz nostr:nevent1qqsvvp5wg5mrnc4226c9ukl7kydyd4v0zgte24nff9l7qad4wx7xpqgc2x3h2 nostr:nevent1qqsfwqwgttstups774qu448437tn6wx9ffw7l5w5fu5ljs5s7efh0zq7csjfn nostr:nevent1qqs0n9gqdjrant7lx2vd77023kh9csr256apwv2f7lsucewuz0kzwzgtmxda2 nostr:nevent1qqsreqlk6ncm7j0zsy7ym2kthv0mc93vgjl5l5jkn3s083ztswsujfszcyhyw nostr:nevent1qqsznlsfkf7ptq4rnegqsd0uvz38mmtk2eeshkmw4y7z2klupzrmgqc2rhluu nostr:nevent1qqstfheaq9cfq96w8kyvwc4herjnt5ehru3zen2yjfh4muc8zx9kmtgehnpyc nostr:nevent1qqs8ac3g79el94kgudcce80h6j6u3nnwagh2rgh87fu0ffky09tx6ugsyxd7g nostr:nevent1qqs0vvczfx44sk9vx7f7fd0l5d8nu9jp9mgv8n0n4rx03ytsx9rh64cml8am0 nostr:nevent1qqsyrk88pql3s2ue85cuwr56pude6f7ay67ylymmtezxdl855tu0pfc2sdwre nostr:nevent1qqs06nhur8vlwf2evmjt2fujamcka38v5krpzfs0yh0n7lk25vtj03ct8nxy4 nostr:nevent1qqsdetdugy6me4l44svtrsy4nc6lsvy8fha9824lca5v9ejdfdasclqd9jf2t nostr:nevent1qqs22th6z0g63dswxjxfwnk92tmpzafec4p9j93cw99tvelervzj2ys3lrsgf nostr:nevent1qqswyktlpagzpjfmv7ldtgkpdzt93zt76s04sa96ngkl976wjpm3dagat2pny nostr:nevent1qqs9pv0457acvajt7ln7tlq39nhlt7tcn4u2l8pvmtjm0f3n3ueuvggxtjsq4 nostr:nevent1qqsztv6rh9s3mx3h237nywtz3z86w6ydsynyp9nzyu43qhuejx5kj5cmc4sv4 nostr:nevent1qqsdu6aqu9y06pw9uk5zah408f5whnuunc3eafmemh5pfeyh20gwc9gr2m00g nostr:nevent1qqsdctkdrz4d0vnendwrekj9uhfw4lkxfjny2gnyrmjvgn0huj3u2xc3aavvw nostr:nevent1qqsp477v4mk2d4qvpj4xt6ua43rj53eqs48qk6jh7lm4c300fq6nm2qxmqz68 nostr:nevent1qqsfgl3x0mv25ytjtr0p5vq2acm4hhnmuxynwxe9a0whvvylsff9ajg0r6du2 nostr:nevent1qqsyvy3qd2hg5tmatgzgzrw9nuqk7tnqtuzzvxhfj7cf9mn06nsq3psxv56se nostr:nevent1qqsgx7lwjaj65ey59m42lvquam85l0vxvx9fcky43nhff3fxy8t7a4su60nr7 nostr:nevent1qqsv6g20rdeq229sfanduu2c497gp9gttejyd9hcpalm4u2f6af3gjc8ynpjf nostr:nevent1qqsqqrmzka388vxuq3ly3urust3svxr7lewxjnhul6v2f9na0xwr3ncxu638f nostr:nevent1qqsxdx9heupdzvhepkq52j0655p94j5w5z72hsy9dcst8h9dgcnq82qwssgfj nostr:nevent1qqsrdvpmljkwdxf4m8jj3ju63w7f42cy869ukwhmgxk5u47vr9q4vsgg54903 nostr:nevent1qqswyy7rwkrfv0q98tdhv43sln0m6gt2yy585m5km70ylxds76g9shst6r9e8 nostr:nevent1qqsw2e5a6hn8hca8xe0aywrgrgd89800xy8680f7cmwc9vtnag47jwqxplvu0 nostr:nevent1qqsywxjm4ay8lcxqvrxqvfgfcfsck29w67uf6fpwas0u2vvm5e772dq6unz4j nostr:nevent1qqsxa9w7lyydy3kxwnnm0a8w2vzjt2px7xklegw2apyvr68wgeepq6qjvmm32 nostr:nevent1qqszt2x6zft0f39yxu2er5qhh7z09xh67kcas9cunwshx7pz3w2xlzg8w6yyx nostr:nevent1qqsvj9q04sw0hlwvfc9ul7yufjd8uy9v0zlhlplr36u9r9t37ffl3ggtx7ard nostr:nevent1qqsgwj2umphzxm82njqzqhm3ujhyept9wd5pvxyzl0u8yctvh4feugcl83uh6 nostr:nevent1qqs93wup3yx2l85rs427uzucujaym9xpkrq6frnhyl8cd9rl8atp6hsak3a3t nostr:nevent1qqs22gxegsg8jwqzptdu9v0m0z9a33tnr42asuujp880qegvakdfasqzzz8tn nostr:nevent1qqsvx3na0fj2k5z9n9jjmcfnxjscq4j58mhpk9yd5ga29z7tq5rayug2pd030 nostr:nevent1qqsgalz2tjnszu03qja9tqmh3fnfhmpmdav9khcwh9506wq9dx50s0gqxe550 nostr:nevent1qqstd0rl52dcjacw8v072e40kc54nyygv436fkja6k2npka0h4x8qhgg87n9y nostr:nevent1qqsyj0hhcgdj3s97zvdnlpwktru2e0f6g002674spyyektxqxky5mpsqym78u nostr:nevent1qqs8tyugskp6gyl89qeynpjp485vsfpltyqx0v5d6cvuacv773q9eqquleude nostr:nevent1qqst2u3y6w830ef6a3sp66gxceryenl3k36ch36mvl9e2d6jwfmgkwqkv4v3e nostr:nevent1qqsy8qhhxhh36xq4kaksyhxm2vy7vuyujrjdxu9m80mw889wx0va3eghz6xc6 nostr:nevent1qqsz7spxfkrzawcwge0hqt9l2q6kc5fc3s5h7pcwj8kqmdtgwsft56q32ezp9 nostr:nevent1qqsrtj4xvtx6tdjv4zmm6axugf29t8xrzp2nmdyh09rzfmaukzp79nckyr3p6 nostr:nevent1qqsrthfeuwsw8ty32lgk6jxqnt2mcr2g7sajze29tyztzys0lxavhkgn609w9 nostr:nevent1qqs8afxujdxjw2jcdjtfsmux72xufzwhhvtc6f44e4yawlcygu9mhvckpdr2f nostr:nevent1qqsfuz3xezyq9e3y99wz6u4z68e09ult0urcyk80rrd4w38jxrcp08gh2hp8f nostr:nevent1qqsrc9nth6vef28sylzxsp7a7ydzqq3slsuas2ydcm4chz76erzpy3qu52mes nostr:nevent1qqsvqr903utwyynxkqyt3nf4jd3gtk355t0rfj6vec6yfp5huqvu39g5tt923 nostr:nevent1qqsgs0alua2ftak3yjp2dkvaxtxk59q8jr6fl3z02z9dt5ecalgjsmqyvpnz8 nostr:nevent1qqsx7sg2tshm7fgku6y86krp2sfvk7evua8mzy86agqfrwphtf5zk9q0rszzc nostr:nevent1qqs95ztf6g0w0k88d8ts5zcc72sw2f0lc0anhcp0f590sxrya70vlas3p0fzr nostr:nevent1qqsq4fsrzz7r60qk7lhmpq9j3e38edee4uuuhqnlpgw90dmqyz3jkscwh3emm nostr:nevent1qqsgnsekfcu53ser5pdnrfpwghsjl57r69xdgjnrn0qxflrvwhv0yxcnw8yyu nostr:nevent1qqswwf3wnj082vrpdjzjd8th0lkes6rdvtzgx0wfftn9398hajvypqc7fvpxs nostr:nevent1qqsyjdhjarz0dmpzpqd0ywhmnyenhmmy28lwj8nkca9av3fxme3s4xsc459u8 nostr:nevent1qqsyqkuylp78memrx58atm4pjggfjpnqmv2z6u0unngpgm89xrp7wtg0qtdus nostr:nevent1qqsv9sdnzjpk98ezcldylxmp7cr5207uxq3em0qdq4mxlc9rw3uflzgsra6wt nostr:nevent1qqsqalxng8fyvyzm5x9rvmu8f6g2mc4fvl42s8qks3v23admjjva9rst7th07 nostr:nevent1qqs245rsx9q22ycamy0dcm6p8gmawzlwj8eq9lp6v0kw96ssdzs2zxswfywrz nostr:nevent1qqsxjvyqjmy9h42kz5pud7uhl87kj3ceagdv4pseyjgrst9aj4r45nqxpwv47 nostr:nevent1qqsr97gg0jm0f87dqvt5dq97jx32uj004lkvapvkqy59wspuytup8zq6skp4k nostr:nevent1qqsy7xuzq5dewwfwrvwannr6vvdxhkxg7njjhqd435nq2k4vcm2ecns4d0agk nostr:nevent1qqs9e5ztm2fhqzm0283u2mzkvgnuv94cvx2h8p0946ch75g03lwr7xsg8mqt7 nostr:nevent1qqs0fvyf9w00k7cfdr7r8hptptx5t7q9gchw40twx24l4e7jcuv605gq34ugz nostr:nevent1qqs9zswmvckn4tke053m9tvhurpf7pwuc3kq82evun9vmvczdz9r5ec95k43c nostr:nevent1qqsrxpxjylc2fjtvwjvt7grk5ae5mwtsp9frkemm2lygfhqurfnfqwcm9k48f nostr:nevent1qqsw6p2j9g9yq0lh3d794nt20flzms2nyvq2752ypfwj2rnlx5sw4tghd5rvx nostr:nevent1qqswrv27dzmtavpcz6d9aphrg8anarhv7jvzfw3twfu43j03qahuc7g3j7pu7 nostr:nevent1qqsvqjgqkw0nfj0yph2ahgfhutw28u5ntyv6s8sz7lxn4jyg6mtw99ga78gwz nostr:nevent1qqsgp93wmz9uyzmzwunh8zvaz8wndg36x04kryw565fwgs6glprlfjqxu537m nostr:nevent1qqszrqjw83xkxdwkp9k45e5fnulp7gjf9ct5zqwxuy8e0mdx2r9fsrcdyay6n nostr:nevent1qqsdyvrhkvdwz6m73sckckr4esauq09u9dhphskxa22kl408gkpmdmg4f85pz nostr:nevent1qqs9g7dhjwlnludgsnkutdf2mnuc4tvagn4jcg7z4uufr3h2w9jd5zsv777kv nostr:nevent1qqsgdwljd9dynp9zd6c2c5l6fyy0j8sh5c44tv55rn5l24lfcq0pz3q2r0hmw nostr:nevent1qqs2atfxw3lzqtawhksqdvzqx7qw3xgp30knlks6lp0rtzhhdczafdqugctck nostr:nevent1qqstr87at5uetk975gwa26evejf9uuhdja84uc602dq7u3ktgfculkc8z948c nostr:nevent1qqsw6kt9s9hqc0p6cd97gxgfdgntdc4kwsf06t8r5q8k7syllr5nffc3e2ved nostr:nevent1qqs2vvsyxxsf73g68nnfkpskyjrhd655852w9w39m4t9yfxk70t2amsqtvlc8 nostr:nevent1qqs9qha3elys5qneel0rlt0s5ch6y6hytt8umpp25knpfu5lm3kvs8snxet5m nostr:nevent1qqs2gkprq3kd4dqf7lzqhg9mgqa9dnagjgaresvgcv63syf0zma0jagdcykl0 nostr:nevent1qqsdn093lcfapk0ke2zqe0982yx66auxvnjklq0ytsxmv7txsn5l06q76jefa nostr:nevent1qqsx2yxa4y7u4trxgtkyvp4jfssdm3lfrtkk7cpkewnpuflq522mkccttn0m9 nostr:nevent1qqsfpphq39tphc0znfdvzty88fdejm4wjr5l0n7ksld3vff0kuhak2cas8yhv nostr:nevent1qqsfvzmk7cfanupzthrjh0t600z6szxj0mz40hrrm4rd7kwqqcehrec27k2qw nostr:nevent1qqsqamgz56h7lqg96p3a42mhr9f7rxjprpsaawz9n2uhgh8n7kaukvglw2xvy nostr:nevent1qqsqt3wp8htyhre4d9n22ldml7k9vs655h55n8758yeenwnc2c8yxmc4fn77d nostr:nevent1qqsrurt0gcz8jzlkyqahz288ex3mqwu8tyh0rcpwlrmu5jckhj3wg5sd6m3a8 nostr:nevent1qqsrsz2uyqvakvwpkne2aqhl3d9yjjyzz2wemsj6vv63rcvcylra6cge70xu7 nostr:nevent1qqs93dzpp2acdw7aq9nwtjg4ap6ytjrc6z99mz0x4l6gq2arpd4r8nq3vzw6u nostr:nevent1qqsvam60cggvxtgxdelm4ja6n8wkqjlsdvwau4yqpr67q85jrc8fmcs6tud72 nostr:nevent1qqsztc59n4p23tw3zwewzn88nz99pwal0fh37aw3gg3ymzlg8np5ghguh0r69 nostr:nevent1qqs9p8k384u2qmugnzusxnna2ge3wldg4rvs895zu5pq6l9df24h0ygrytc6v nostr:nevent1qqsvh2lfpxvp7x7cs9d8ttr9ra9m6xl5405lal7x6f2uf5xymlz6j9gqp4ut3 nostr:nevent1qqspndcrk2lxd86tvdy3yd5gqmytvr543pa2cpsgmjylprk33zcsk3crx34t7 nostr:nevent1qqspr3nmus3ch4zy8js73gvqxyz5p5ed8ch6rxl4ymqs2x9fql4ys8gn9x9qw nostr:nevent1qqspslhp7kzfgu0t8rgf0nhm0s4rgnj9rx329vuze8f62r0qmtpx8xcm0tprj nostr:nevent1qqsg3hk5mdre8ny2fpp5xwct7cary359ld8cx97f5h388epg9flwgeqfuzwzy nostr:nevent1qqs9d7dqsqfp2cv3mstn7fnwdsemtct44wan43uy4kkfchd49l65lxg5h2cjz nostr:nevent1qqszn7ycnfn9suns5xxam2207v70ast0w07yq9shwzv6e9cuvz2w0vq22kafd nostr:nevent1qqsdyfrj2n0mxtkgmdy562qdahj8vzrt8drjphvw4cfgp45qvwq06lgu8tzea nostr:nevent1qqs0tja3rdn95q3plklyvz2swkyj8wmfnf5sese5882mh40yj85mdkgcx9sdt nostr:nevent1qqsdfj4zf20wpg8ldkdt2pdnr0tjmjfgc0mz8e2t7l4kf7syrelxhnqnplcq8 nostr:nevent1qqsp9wva4ujkvzyl7ve05h95quq6shnvsgexkw6n588n8wym6tutujcrmdcp8 nostr:nevent1qqs2f6t7et6tag8qms6vkzwpw9tn3fvxqp86hh7dxrr4pxfeeunge6cgaykdg nostr:nevent1qqs0lnhgz0khlsjjq6404p2hug3pwvcqt6x2x6l7yfmfqwzxf364y2gawq8xh nostr:nevent1qqspj2ar7xc4zs3catcks73ppvs77sj59zfdd6vu0h99ukqdt7wf0cgpdcq7s nostr:nevent1qqsyytgaxazjm8gnj64g5l4hushyu9040r336xs4sl0s79jet77esyspcmfel nostr:nevent1qqsw0jdhk5sytywvpn4gzfy6ahrjsmarellyjwy6vm4t82l83x9h4zca63vzu nostr:nevent1qqsgs9q52e920wx0gsy29egqch5x6aey9mtt3jl8kv340uw7lmcgceg43ecjv nostr:nevent1qqsdj0awygazadajkysga3anet6s38vrxrvj55kvhyguvyagqxk2z3sjla65v nostr:nevent1qqsypmjgxeqt9rah3sfxraudpdfhfj0k0sut39n07e4xwtpw5fmju8qfdh234 nostr:nevent1qqspaqxwrg9trpcg4sp2gtjjw6jw6u2rj9yu8al2hscdfdv8ra60f2s5z56vf nostr:nevent1qqsdp3kg2f7ena80zkpw68uc8x4fatccul56jf5j87nhzaqk8mwgsccczcc57 nostr:nevent1qqs9p8wdx53y57ysg39jjgzt5gu67ntqq0u8zv7gsgp3v3xsxw6ta4ssvh6vp nostr:nevent1qqsppejxz438ummams5427fzzfg4lnuswfww6ha2yapf4kkl73mhm6sjtlans nostr:nevent1qqsfewzswnqzwkp76qp7rga0007v2er0s797eqcd2z8cee57u74xv0cn290jt nostr:nevent1qqsq9vjah3gtma3gz99y4m7ey6df8p34n8u572cmaqzwq95xl9xm72gwfrqg8 nostr:nevent1qqsw2qm4664k4f6633j57t7vrwxn9rht6x0sf2suaejjgttrgxm52ccvv9lrj nostr:nevent1qqsplx6sls8ga3eez376m6umwszjj6lmuardvzs72pyekgzyanf0c5s5d5q2r nostr:nevent1qqs8cast93yvaxl0zj20aakl6h4hz6wx8vr7sv4cy4sz20frpdj9ezslrvq4s nostr:nevent1qqswku45leeulqe574ustynud357jwneu3t02qatw0atr3zyclxzaqscxj0sj nostr:nevent1qqsfmsqlukjx47aumecfhq979c53mmyv99ftfgj2luz9h8fe54m9x7sg0jcy9 nostr:nevent1qqsyquj9cquhsmzescerqjyur4cct2eatd6yrp7cxlfjzr0502s7fccyggrwq nostr:nevent1qqsxxurfn8xd83nz52jw2z37cvc3pdnsxvtp6fn9wkzysezh600wl0qs3mdws nostr:nevent1qqsdalre0nscl5mcg8z5tj2rwc08qpjphzvdy56fqvshtuuuvaqgjtskgr03s nostr:nevent1qqszln2q627ef64djy5pn05jzuh8alnuurl4z67fagtehucfg24pkscrgnnth nostr:nevent1qqs0ztxssvt4kt7kuwyts6z4pm7k46undqpccfvn6r54snuzax66z8qw8fyvk nostr:nevent1qqsw8h3n6xc6f5tpqtcqud68tdczruae32hqwdenes34k5dup6kqxqgnwawsu nostr:nevent1qqswjh2qdz0dgmj3va747seu5eu9lnr49zt9kws4lx8lczw74x5gj0c70r6lg nostr:nevent1qqswvkdqtkxy627hvxue8jsam0m93scj7p6jjgqh0mn2r6m9u4pfq9g6q882j nostr:nevent1qqsd4uhh42gq9sj4vtwcr6cnkpwd9k3mzm0g8myakg9ynglfkxyvlqca64zcs nostr:nevent1qqs8wnayqec04sqvl6rt9kyylty09jng6g4ktv8h594x95vn352a43suhqvtu nostr:nevent1qqsfsguft8a77ttqff88emq8dfrvqs8v8lc8ka5d2pjt57wesq6tk8cz4a84y nostr:nevent1qqsf99szvuzldnvgg49dnvlttttd89xpkc9rhfn4wghsfwalrsplesqvw5tpd nostr:nevent1qqsv4vptazj68zgxvf8z5zy3ptz8vwfgkq99a65l2s7hslc5y8vafequjwp3t nostr:nevent1qqsqa5zjxcdu3t7qxlqnrgcgyvftwr8adns8eq6anevwalawpshjs2g48e9gl nostr:nevent1qqsx92uj3cg62w3fsnys7vepwvf9x347hdm3cgww4nvqetdc8h6y5aszzrs7z nostr:nevent1qqs97wu7kt8g3u9sp06rduksjh22uz28etjv7d9fqccfzh2rcajc5ssx6660y nostr:nevent1qqszrjy9qltpxrmqelm39s8f68p3mzq3mz6hy535kt576ryd4xj45rc6m42vz nostr:nevent1qqsz3tzzg2cp2qqu0wpcvg3lgdz7t5jalrl3z9vnhh4qxacx3mt370gma2eur nostr:nevent1qqs8ys6zj6ta8c9m4f47g04tyc4s0uk3rzlj8nzyvn88rqjsak8d3acd9m46w nostr:nevent1qqszc99x43vh4y6g6ufa6s4ffrppjgjmun27je898u90fdml6p2hz8g3dtnhp nostr:nevent1qqs8k903clgruktvagvadtf5huyx4leedd0w9shcrgwyg90y0g7tzmck89mzp nostr:nevent1qqsydxc8mzmsf0qyx8paweap69qaw8fgssz56xmg5q6grxqee2uz75gszqegy nostr:nevent1qqsdscwrfvt0fr0847qd2edna8lduuh7fk2g8jhktvr0r3gmrs7l4kgw08n9r nostr:nevent1qqsrf7tduyxx0h3ywed0pfjtnf7wxjde6xqzeu9qczwar50ptql64uc2cytg3 nostr:nevent1qqstnwlulgt689cwygappskjlexnt3ejzlh380w6gsx93e4mg2smt8gdrz8l9 nostr:nevent1qqsdmke8e87qvy54lz0u3twz36wsz02t8cp0qp5v5hepwd2nf4lfg3seyp84n nostr:nevent1qqszrr2k94yve0v5lxnm82x55vkwu3g36eqf8nya5cgxz9utwc7tlvccuu63k nostr:nevent1qqswgyad2qu6ltmnfasetun80hctvkx5npnwqamse33auvpm2tev5usvx5xd2 nostr:nevent1qqs9cxp7w8tjzed2aaxfscglmac4ddcqzmt667pv2qxck6zmfs7gmkcdxpzps nostr:nevent1qqsgdknwqqa6gkr0x403s6eh3xxjxqd0gy8hxp9mkxkuffaxqmffk9gya2fhh nostr:nevent1qqs0rq7r8s56jhnrysnkg4k99f0q96uphl7vjvjexaazufpzmjl2ldc8ppz5l nostr:nevent1qqsx24ratma6qgt65vj30k5vtcf8ls5l9swrxhe82t3f7xev92n2ckgxepk7g nostr:nevent1qqs06jpjgw56t0xuuu82td6sd8yjnpu9d78z4vvxc6q9gxq5axh0n6spryvch nostr:nevent1qqspa75xvvkw6zpavvrgp3mk30y6shjsg43v0yekk2nqf582xek3mvqr4vjw4 nostr:nevent1qqsvlz88ahc6uq7yqfuuus2vgk035ywa582amt3umaxq0a4hw7sdvzchnavfj nostr:nevent1qqs908tjsfvv9hwn64v800da3p2lkgwcwv695eksc6hhkavgqk6wleg3ue08p nostr:nevent1qqs97hyy2zm3lsah7r3d6u536xf5wn2w8afyqlz7zgqwmaqsn0flsnczp2q4f nostr:nevent1qqsg2hatn34sm5qpsxsykdk35nwrp68n5ggjlgac2qrhjxrzp6vgvlc8v8nuj nostr:nevent1qqsyu8evwrh0kagzjcpcfy8nhdvt5gdnf5q0pex7vukagnm3llzljycp4d3h0 nostr:nevent1qqsvj2hnvgme0zzf8p6u0ehlk27z5yn4zwlravn9ft3smgks77gnxnst533zf nostr:nevent1qqszhfx4aq8qllq3xd2cnyqyenwzu0gysqr9fdrwsx73zp5rv9uflegmeqz70 nostr:nevent1qqsqmga4dkcqkw8tzugg23p7qck622wlgxhhtfshppuzpt8a8xpneac9avf4s nostr:nevent1qqsp3tf4vamjezdpcc4d9jxjrqj6mpunehw4n0p0m6cwdzxy2rgllyqeves5g nostr:nevent1qqs8vnfc2uuvsce0c88kyz5qpn954zv5wqdksprq20c84x0m8axndlg3wc3v2 nostr:nevent1qqsgvctjju645q2yuleqmmt7ku4pwjrf0pjgher4um87k6t33h4yycg5ewtzj nostr:nevent1qqs0ud2vpw9mp59dq5pm9hyxhu6vye9z68k9syrhfjsdqed89zhureqycl52m nostr:nevent1qqszkwqymc8xhvn0afnw9j4ax3dts6e7rv5v9n5zhqmxuxgqmv09kns8rjn00 nostr:nevent1qqs8e6kcap8ae2es6t34053pfvpkeucpt34ve6hhrfgnvh7j2fa4u7qnxaaw0 nostr:nevent1qqsvjd08zysyj93ypsze3jraww4hjdqgr25kzee86c2mutz08rzjgac4k4ef0 nostr:nevent1qqsqqgqnayjy80wfa3qkws83a0ef2rxfnpdet5f33ph0csz3gcqap8gjjnyf8 nostr:nevent1qqsp5m8ar6rsuaah2s8mz8knsq7fm3vlqk60pkvs9xvgugxt99c46wq8va8vg nostr:nevent1qqszptmufg2y38v2cy6v57ptnf27mg7kvh5hmp8uhk9cjwl9m8zrnqc6vf5dx nostr:nevent1qqsg9jl952dq4qvzyfklverpt5aqkp6lmw04kzz6z3zz3n9qg5unt7qjchphg nostr:nevent1qqs9e8jgsv4kyulgz0r7x5z3mxuw2l5ya8las4tkf5z8sy97elvud8qq9s88n nostr:nevent1qqsw0w3f0jvx6pa203kqm8lmhaf2qq69tvnt0f7pedp8ksmtazmjunqzvz5d5 nostr:nevent1qqs25shxc9l6mcudx8su646etmfmx7ywv87dcewjxu87qax49lnkylglpk47n nostr:nevent1qqsfj00j5sk7fuxuxxt8wpf9d60vysfqk0mz53478tfvccx4s4ys7rc2l0uzj nostr:nevent1qqsfwdnw4qfc7j3hnhcrxdu7ecxvgpjmveftu9g29fxg4ra7k9vvehgd744hs nostr:nevent1qqsfqm6phetgyjr7f5zt67gq6k8dv2lgh7j4leax75wk0ry4wfral4sp9pv56 nostr:nevent1qqsrtl8wtsxcrmncwkjrshm3d7ys633zswz5y7r530ywlfpsjk8qtpsprkh4r nostr:nevent1qqs2mqqlpq3s5scaz9dsvn4vnqwzyyp8wtxe43k2pmlfvn9qk9ck8ksts3ll3 nostr:nevent1qqsyl7rhny5et457dm6l23z6hercuvv5hch7pm5xs4v2ekn44c27zaqjpx0r2 nostr:nevent1qqsp3yaj6hzzfd840kmvsct9nw7y94c7pdfw2cnkdgqwaswx2xr0wcqeusc5d nostr:nevent1qqs2ze6chukganrfwmnspce3nuu02zmh0r4nn3z5ed62xx8qtvdjfzsyzp75l nostr:nevent1qqs0kq8eevn32v0karl0naywzeqck2m9sqsync2p0z4phc2tdx2mf2cqer0ws nostr:nevent1qqs9h77g2c3t72q4l9n7e76me8488qkdxyjw2l95nztx36kzxd73tjq973dat nostr:nevent1qqszq5lza048954nq30pwfmqaapentajp7zjqmjtw8zvh0zunt662vsvuqzz5 nostr:nevent1qqsxwhlaqhtkhpsn209e0a7lla3upc0gyse4pyg9np44lc7vg0nuzhcjtljuf nostr:nevent1qqsg2a04k9r6mggptyxjjt9d5whjull77d3aw8xfel8e29eeje8ugzqd8frp4 nostr:nevent1qqs8sk0p79mn9cgcjgxhycyrtq0fxzxepvlnd706mfyrhyyj7jqyk5qhuqfpw nostr:nevent1qqsx9t68ffff4cnz2z36n52eezk6ayqefud340j5thdft7fjt2upd3q0vyzc7 nostr:nevent1qqsw6cn4w95ku93u9atcrduz6st8vuwf9zf4qjge3w6xkpa8lp6rzesufawc4 nostr:nevent1qqsv9yjmw4gq3xgxy4fq02rqk8gsqxk7wyh4uvhppezxrcp7utacdyq233x8j nostr:nevent1qqsrlgvn2uu0zueultxv7stkaalw7vdu2z2ukvttfdw5sj2y865g50gws5cds nostr:nevent1qqsgarz5ppp3mn4m77t2xzzjqq0tps5sjxuve3k2w0ylf55vd4a4uqsxvd9xj nostr:nevent1qqs95z85mhl75j27g5aqw8s3ntm5kasmlglsg3w3u2h6lncyrg0rvkqc5zgjf nostr:nevent1qqspdzkrtk8h8h67egltafs7s32j9vvzxcpycm8dd689e572atr8xfg30a8ce nostr:nevent1qqsq2kd7c2flkrwqz4344gpwx4al4ekrr9wxe3kt7rjz7amcutnzcpsej2atv nostr:nevent1qqsfhz5rx22f5m3x60dpe08fjjpu7mrkeqpq0z2jjn54yh3uzdw257gpws5nq nostr:nevent1qqszc7l3tp70y0ml3zvppuyj2kvs07knxq6d8je3saemv2pgthc2hgczy6pw9 nostr:nevent1qqsta6ec23jz9jpxg8cfy0ae84xcqrcka6u7vsknjfwsq7ec9cx2k2gyfmgup nostr:nevent1qqsyad6h6dpykmhehuaseh2cu53reqf4q5ff7g0k494jvqwjua2dmesxdjwtq nostr:nevent1qqs0g5nm4jajj9rfzd42cueqhakyevs0zg3zsmnv2y6va6dqfnzx79cds0u6e nostr:nevent1qqs8kzvkgq7judfywvt6vaekwn9azslavl75xe40t8wnzhtar24p3kcndx7ld nostr:nevent1qqs24ynaypvt745e0nmdux5cjt57fxs9wtda3p7nnn5jslmxv9g9q4g2zt603 nostr:nevent1qqsp2nujt5m6ypp5cn4yauz58stjn4m3jguecklw7hgyjdg73zc4ddsdz32p3 nostr:nevent1qqsx9sqkyv5afv03mdc2w0ay3t0u872nme3c6ryvs48r5hd7gjg6raq9qa7sq nostr:nevent1qqsv0jsyde7lndup8czlzft8dw9mg06w3evmhtz4ezj2zteepzxacwgdsv7jw nostr:nevent1qqsdu644w6mrn3u468vzuhprckkc8xjqznev2h602ft74c76vx2350cgrqv3a nostr:nevent1qqsg6v7z35vjrfrqkly6fewjjk0yxd5rwdepp28t9ghnt3s9kpdynhce8w5t9 nostr:nevent1qqs9l446svwqwr5h54ygrceqvf20guta566ezwkneu2hx49ha5vdalcjevmxl nostr:nevent1qqsfurxh37ap65w8c87ju4pr4jr9245drjf3ua4l7hc29429cse7e5cw46m4c nostr:nevent1qqs2q76mjpqq8p9kz86869gs65ccrjye2uml887tdau9znqg43k7phg0mzlx2 nostr:nevent1qqsdq24a356ep48la4yt74tcyt5as37ux0ejxfzpthzd5y85ws0n4xqars3lu
-
 @ de6c63ab:d028389b
2025-04-28 12:20:45
@ de6c63ab:d028389b
2025-04-28 12:20:45Honestly, I didn’t think this would still be a thing in 2025, but every once in a while it pops up again:
“Bitcoin? Uh, I don’t know… but blockchain, now that could be useful! 🤌”
“Blockchain is one of the most important technologies of our time. Maybe you know it from crypto, but it’s so much more. It’s a way to store and verify data securely, transparently, and without a middleman. That’s why it’s going to revolutionize banking, healthcare, logistics, and even government!”
“Blockchain is transforming how we store, share, and verify information. Its benefits go far beyond cryptocurrencies. Understanding it today means preparing for tomorrow, because blockchain is guaranteed to play a major role in the future.”

Blockchain
When people say "blockchain," they usually mean the bitcoin database — with all its unique properties — even when they’re imagining using it elsewhere.
But here’s the thing: blockchain by itself isn’t some revolutionary breakthrough.
Stripped from bitcoin, it’s just a fancy list of records, each pointing to the previous one with a reference (typically a hash).
That's it.This idea — chaining data together — isn’t new.
It goes back to at least 1991, when Haber and Stornetta proposed it for timestamping documents.By itself, blockchain isn’t secure (you can always rewrite past records if you recompute the chain), isn’t necessarily transparent (the data can be encrypted or hidden), and doesn't magically remove the need for trust (if someone logs soccer scores into a blockchain, you still have to trust they reported the results honestly).
What actually makes bitcoin’s blockchain secure and trustworthy is the system around it — the economic incentives, the ruthless competition for block rights, and the distributed consensus mechanics.
Without those, blockchain is just another database.
How Does Bitcoin Make It Work?
To understand why, we need to zoom in a little.
Superficially, bitcoin’s blockchain looks like a simple ledger — a record of transactions grouped into blocks. A transaction means someone spent bitcoin — unlocking it and locking it up again for someone else.
But here’s the key:
Every participant can independently verify whether each transaction is valid, with no outside help and no trust required.Think of every transaction like a math equation.
Something like: x + 7 = 5, with the solution x = -2.
You don’t need anyone to tell you if it’s correct — you can check it yourself.Of course, bitcoin’s equations are far more complex.
They involve massive numbers and strange algebraic structures, where solving without the right key is practically impossible, but verifying a solution is easy.This is why only someone with the private key can authorize a transaction.
In a way, "solving" these equations is how you prove your right to spend bitcoin.
Ownership and transfers are purely a matter of internal system math — no external authority needed.
Could We Use Blockchain for Other Stuff?
Could we use a blockchain to independently verify medical records, soccer scores, or property ownership?
No.
Blockchain can't magically calculate whether you broke your arm, whether Real Madrid tied against Barcelona, or who owns a cottage in some village.
It can verify that someone owns bitcoin at a particular address, because that's just solving equations inside the system.
But anything that depends on outside facts?
Blockchain can't help you there.
Why Does Everyone Stick to One Version?
Another big question:
Why do people in bitcoin agree on the same version of history?Because of proof-of-work.
To add a new block, you have to find a specific giant number — the nonce — that, together with the block’s contents, satisfies a predefined condition.
You can't calculate the nonce directly — you have to guess, billions of times per second, until you hit the jackpot.
It takes minutes of relentless effort.An invalid transaction would invalidate the entire block, wasting all the miner’s effort.
If the block is valid, the miner earns a reward — newly minted bitcoins plus transaction fees — making the massive effort worthwhile.
And importantly, because each block is built on top of all previous ones, rewriting history would mean redoing all the proof-of-work from that point forward — an astronomically expensive and practically impossible task.
The deeper a block is buried under newer blocks, the more secure it becomes — making the past effectively immutable.And again: each node independently verifies all transactions.
Miners don't create truth; they race to package and timestamp already-valid transactions.
The winning chain is simply the one with the most provable work behind it.
Bitcoin and Blockchain: Inseparable
Bitcoin is created on the blockchain — and it exists only within the blockchain.
Ownership is defined by it.
The decentralized management of the blockchain is driven by bitcoin incentives — the pursuit of something scarce, hard-earned, and impossible to fake.No blockchain, no bitcoin.
No bitcoin, no meaningful blockchain.
Can We Just Blockchain Everything?
Alright, so what happens if we try to apply this system to something else — say, a land registry?
Properties themselves don’t "exist" on a blockchain — only claims about them can be recorded.
But who writes the claims? Random miners?
Where do they get their information?
They can’t compute it from previous blocks.
They’d have to physically go check who owns what.What if they’re lazy? Lied to? Made mistakes?
How would anyone else verify the records?
Ownership in the physical world isn’t a problem you can solve by crunching numbers in a database.Suddenly, we’re right back to needing trusted third parties — the very thing blockchain was supposed to eliminate.
And if there’s a dispute?
Say someone refuses to leave a house, claiming they've lived there forever.
Is the blockchain going to show up and evict them?Of course not.
Blockchain Without Bitcoin Is Just a Data Structure
And that’s the difference.
When blockchain is part of bitcoin’s closed system, it works because everything it cares about is internal and verifiable.
When you try to export blockchain into the real world — without bitcoin — it loses its magic.
Blockchain-like structures actually exist elsewhere too — take Git, for example.
It’s a chain of commits, each referencing the previous one by its hash.
It chains data like a blockchain does — but without the security, decentralization, or economic meaning behind bitcoin.Blockchain is just a data structure.
Bitcoin is what gives it meaning.In bitcoin, the blockchain is not just a ledger — it's a trustless system of property rights enforced by math and energy, without any central authority.
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 82b30d30:40c6c003
2025-03-17 15:26:29
@ 82b30d30:40c6c003
2025-03-17 15:26:29[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
[32]
[33]
-
 @ 06639a38:655f8f71
2025-03-17 14:59:40
@ 06639a38:655f8f71
2025-03-17 14:59:40https://ccns.nostrver.se is a (Drupal powered) website that I started to build in January 2024 (source on Github and Gitlab). It's a fork of an earlier (abandoned) project https://cchs.social/.
Currently CCNS is a link aggregration website and for now it's only my who is using it to save and share Nostr related links. When you post a new link, you have the option to cross-post it as a Nostr note (example here).Kind 39700
Last month Jurjen and Abir have started to work on a social bookmark client built with Nostr (inspired by Del.icio.us from the past). Earlier this month they changed to event kind 39700 for broadcasting the Nostr event with the bookmark / link data accross the network. They did this because Sep already created a social bookmark like client called Pinja when fiatjaf raised this idea.
With these developments to me it was very obvious to integrate the feature that new created CCNS links are now also published as kind 39700 events to the Nostr network. This means that links are now also distributed on multiple relays as kind 39700 events and are accessible in multiple clients (Yumyume and Pinja).
Here you can see the same data, from left to right:

Structure
The current data structure for the 39700 kind looks as follow:
- "id": "event_id"
- "pubkey": "pubkey author"
- "created_at": unix_timestamp
- "kind": 39700
- "tags":
- "description", "description text here"
- "d", "unique-slug-value"
- "t", "hashtag"
- "content": "https://book_mark_url"
- "sig": "signature"
As there is no NIP (yet) for this event kind, I see some possible improvements:
- Use the bookmark URL as
dtag so it can be used as a unique identifier for every client - Use the content field for the description
- Use the
atag for an addressable event following NIP-01:["a", "39700:pubkey_of_author:", recommended_relay_url_optional]
On short-term I don't have any plans to developer CCNS further, as most of my attention goes to the development of the Nostr-PHP library and Drupal related contribs using that library. That said, CCNS is a Drupal project but all the Nostr stuff is done client-side (Javascript) with NDK and Nostr-PHP is not used (maybe this will change in the future).
-
 @ 84b0c46a:417782f5
2025-03-13 06:44:10
@ 84b0c46a:417782f5
2025-03-13 06:44:10 -
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Module Linker
A browser extension that reads source code on GitHub and tries to find links to imported dependencies so you can click on them and navigate through either GitHub or package repositories or base language documentation. Works for many languages at different levels of completeness.
-
 @ fd06f542:8d6d54cd
2025-03-31 01:57:20
@ fd06f542:8d6d54cd
2025-03-31 01:57:20什么是nostrbook?
nostrbook 是基于nostr 社区技术存储在 nostr relay server上的长文(30023)文章。 查看浏览,采用的是 docsify 技术。整个网站技术无须部署服务器占用太多的存储空间。 可以实现轻量级部署。
-
 @ f683e870:557f5ef2
2025-04-28 10:10:55
@ f683e870:557f5ef2
2025-04-28 10:10:55Spam is the single biggest problem in decentralized networks. Jameson Lopp, co-founder of Casa and OG bitcoiner, has written a brilliant article on the death of decentralized email that paints a vivid picture of what went wrong—and how an originally decentralized protocol was completely captured. The cause? Spam.
The same fate may happen to Nostr, because posting a note is fundamentally cheap. Payments, and to some extent Proof of Work, certainly have their role in fighting spam, but they introduce friction, which doesn’t work everywhere. In particular, they can’t solve every economic problem.\ Take free trials, for example. There is a reason why 99% of companies offer them. Sure, you waste resources on users who don’t convert, but it’s a calculated cost, a marketing expense. Also, some services can’t or don’t want to monetize directly. They offer something for free and monetize elsewhere.
So how do you offer a free trial or giveaway in a hostile decentralized network? Or even, how do you decide which notes to accept on your relay?
At first glance, these may seem like unrelated questions—but they’re not. Generally speaking, these are situations where you have a finite budget, and you want to use it well. You want more of what you value — and less of what you don’t (spam).
Reputation is a powerful shortcut when direct evaluation isn’t practical. It’s hard to earn, easy to lose — and that’s exactly what makes it valuable.\ Can a reputable user do bad things? Absolutely. But it’s much less likely, and that’s the point. Heuristics are always imperfect, just like the world we live in.
The legacy Web relies heavily on email-based reputation. If you’ve ever tried to log in with a temporary email, you know what I’m talking about. It just doesn’t work anymore. The problem, as Lopp explains, is that these systems are highly centralized, opaque, and require constant manual intervention.\ They also suck. They put annoying roadblocks between the world and your product, often frustrating the very users you’re trying to convert.
At Vertex, we take a different approach.\ We transparently analyze Nostr’s open social graph to help companies fight spam while improving the UX for their users. But we don’t take away your agency—we just do the math. You take the decision of what algorithm and criteria to use.
Think of us as a signal provider, not an authority.\ You define what reputation means for your use case. Want to rank by global influence? Local or personalized? You’re in control. We give you actionable and transparent analytics so you can build sharper filters, better user experiences, and more resilient systems. That’s how we fight spam, without sacrificing decentralization.
Are you looking to add Web of Trust capabilities to your app or project?\ Take a look at our website or send a DM to Pip.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Using Spacechains and Fedimint to solve scaling
What if instead of trying to create complicated "layer 2" setups involving noveau cryptographic techniques we just did the following:
- we take that Fedimint source code and remove the "mint" stuff, and just use their federation stuff secure coins with multisig;
- then we make a spacechain;
- and we make the federations issue multisig-btc tokens on it;
- and then we put some uniswap-like thing in there to allow these tokens to be exchanged freely.
Why?
The recent spike in fees caused by Ordinals and BRC-20 shitcoinery has shown that Lightning isn't a silver bullet. Channels are too fragile, it costs a lot to open a channel under a high fee environment, to run a routing node and so on.
People who want to keep using Lightning are instead flocking to the big Lightning custodial providers: WalletofSatoshi, ZEBEDEE, OpenNode and so on. We could leverage that trust people have in these companies (and individuals) operating shadow Lightning providers and turn each of these into a btc-token issuer. Each issue their own token, transactions flow freely. Each person can hold only assets from the issuers they trust more.
-
 @ 97c70a44:ad98e322
2025-01-30 17:15:37
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the protocol, while apps that benefit nostr exclusively via network effect are integrated into nostr the network. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency as nostr users.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria.
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a spec for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (ahem, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the nips repo. No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-
 @ 9e69e420:d12360c2
2025-01-26 15:26:44
@ 9e69e420:d12360c2
2025-01-26 15:26:44Secretary of State Marco Rubio issued new guidance halting spending on most foreign aid grants for 90 days, including military assistance to Ukraine. This immediate order shocked State Department officials and mandates “stop-work orders” on nearly all existing foreign assistance awards.
While it allows exceptions for military financing to Egypt and Israel, as well as emergency food assistance, it restricts aid to key allies like Ukraine, Jordan, and Taiwan. The guidance raises potential liability risks for the government due to unfulfilled contracts.
A report will be prepared within 85 days to recommend which programs to continue or discontinue.
-
 @ 2cb8ae56:84d30cba
2025-03-06 07:40:38
@ 2cb8ae56:84d30cba
2025-03-06 07:40:38どうも、Nostrまとめ(2024)ぶりですね。
記事として出すのはかなりお久しぶりかも、お名前変わりまして「フェゼレント」でございます。 意味としては以下の通りです
1.Fezer(フェザー)という英単語 2.ent(エント)という造語 2-1. netを崩した形、よくこれに打ち間違えます。 2-2. Entertainment(エンターテイメント)の略語、なんか娯楽とか話題を生み出せる人になりたいですね。
1と2をガッタイ!!!(トムブラウン風)しまして、フェゼレントです。
なんとググってみますと、Fezerent及びフェゼレントの検索結果が0。 これは...一種のチャンスでは!?と思って、使っています。
さて、そこで出てくるのが「薄味のキャルピス」と「IVstrook」の今後ですよね。 後者に至っては3年分の料金を払ってドメインまで取っているわけですし、前者はかなりネットとかラジオでも浸透しています。
というわけで、こんな風に置き換えます。
Nostr、YT、Discordはフェゼレント及びFezerentを使用します。 それ以外(ラジオを含む)では薄味のキャルピス、IVstrookを使用します。 そして、NHKなどAM波を使用して放送を行っているラジオ局用で使用していた「テックジャンカー」ですが、使用を停止します。 あんま浸透しなかったわけですからね
そんな感じでやっていきます 最後に、記事最後に使用する署名のような奴ですが、そちらは変更なく「IVstrook」単体で行います。
また、ニコニコ動画及び各種ポッドキャストサービスにて配信しておりました「Small Room Space」ですが、今後はzap.streamというNostrのシステムを使用したサービスを用い、番組名の変更は行わないものとします。 zap.streamでの配信開始は「4月7日」 ちょうど#1が公開されてから1年が経過した日です
重ねて、当名義を使用したニコニコ動画への投稿は「3月8日」をもって終了とし、zap.streamへ移行します。
以上、今年に入ってからまともにニコニコ動画で投稿できていませんでしたが、そのような運びとさせていただきます。
2025/03/06 IVstrook
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Just malinvestiment
Traditionally the Austrian Theory of Business Cycles has been explained and reworked in many ways, but the most widely accepted version (or the closest to the Mises or Hayek views) view is that banks (or the central bank) cause the general interest rate to decline by creation of new money and that prompts entrepreneurs to invest in projects of longer duration. This can be confusing because sometimes entrepreneurs embark in very short-time projects during one of these bubbles and still contribute to the overall cycle.
The solution is to think about the "longer term" problem is to think of the entire economy going long-term, not individual entrepreneurs. So if one entrepreneur makes an investiment in a thing that looks simple he may actually, knowingly or not, be inserting himself in a bigger machine that is actually involved in producing longer-term things. Incidentally this thinking also solves the biggest criticism of the Austrian Business Cycle Theory: that of the rational expectations people who say: "oh but can't the entrepreneurs know that the interest rate is artificially low and decide to not make long-term investiments?" ("and if they don't know they should lose money and be replaced like in a normal economy flow blablabla?"). Well, the answer is that they are not really relying on the interest rate, they are only looking for profit opportunities, and this is the key to another confusion that has always followed my thinkings about this topic.
If a guy opens a bar in an area of a town where many new buildings are being built during a "housing bubble" he may not know, but he is inserting himself right into the eye of that business cycle. He expects all these building projects to continue, and all the people involved in that to be getting paid more and be able to spend more at his bar and so on. That is a bet that may or may not end up paying.
Now what does that bar investiment has to do with the interest rate? Nothing. It is just a guy who saw a business opportunity in a place where hungry people with money had no bar to buy things in, so he opened a bar. Additionally the guy has made some calculations about all the ending, starting and future building projects in the area, and then the people that would live or work in that area afterwards (after all the buildings were being built with the expectation of being used) and so on, there is no interest rate calculations involved. And yet that may be a malinvestiment because some building projects will end up being canceled and the expected usage of the finished ones will turn out to be smaller than predicted.
This bubble may have been caused by a decline in interest rates that prompted some people to start buying houses that they wouldn't otherwise, but this is just a small detail. The bubble can only be kept going by a constant influx of new money into the economy, but the focus on the interest rate is wrong. If new money is printed and used by the government to buy ships then there will be a boom and a bubble in the ship market, and that involves all the parts of production process of ships and also bars that will be opened near areas of the town where ships are built and new people are being hired with higher salaries to do things that will eventually contribute to the production of ships that will then be sold to the government.
It's not interest rates or the length of the production process that matters, it's just printed money and malinvestiment.