-
 @ 93e8ebba:1075c629
2025-04-29 22:52:46
@ 93e8ebba:1075c629
2025-04-29 22:52:46test
-
 @ 3bf0c63f:aefa459d
2025-04-25 19:26:48
@ 3bf0c63f:aefa459d
2025-04-25 19:26:48Redistributing Git with Nostr
Every time someone tries to "decentralize" Git -- like many projects tried in the past to do it with BitTorrent, IPFS, ScuttleButt or custom p2p protocols -- there is always a lurking comment: "but Git is already distributed!", and then the discussion proceeds to mention some facts about how Git supports multiple remotes and its magic syncing and merging abilities and so on.
Turns out all that is true, Git is indeed all that powerful, and yet GitHub is the big central hub that hosts basically all Git repositories in the giant world of open-source. There are some crazy people that host their stuff elsewhere, but these projects end up not being found by many people, and even when they do they suffer from lack of contributions.
Because everybody has a GitHub account it's easy to open a pull request to a repository of a project you're using if it's on GitHub (to be fair I think it's very annoying to have to clone the repository, then add it as a remote locally, push to it, then go on the web UI and click to open a pull request, then that cloned repository lurks forever in your profile unless you go through 16 screens to delete it -- but people in general seem to think it's easy).
It's much harder to do it on some random other server where some project might be hosted, because now you have to add 4 more even more annoying steps: create an account; pick a password; confirm an email address; setup SSH keys for pushing. (And I'm not even mentioning the basic impossibility of offering
pushaccess to external unknown contributors to people who want to host their own simple homemade Git server.)At this point some may argue that we could all have accounts on GitLab, or Codeberg or wherever else, then those steps are removed. Besides not being a practical strategy this pseudo solution misses the point of being decentralized (or distributed, who knows) entirely: it's far from the ideal to force everybody to have the double of account management and SSH setup work in order to have the open-source world controlled by two shady companies instead of one.
What we want is to give every person the opportunity to host their own Git server without being ostracized. at the same time we must recognize that most people won't want to host their own servers (not even most open-source programmers!) and give everybody the ability to host their stuff on multi-tenant servers (such as GitHub) too. Importantly, though, if we allow for a random person to have a standalone Git server on a standalone server they host themselves on their wood cabin that also means any new hosting company can show up and start offering Git hosting, with or without new cool features, charging high or low or zero, and be immediately competing against GitHub or GitLab, i.e. we must remove the network-effect centralization pressure.
External contributions
The first problem we have to solve is: how can Bob contribute to Alice's repository without having an account on Alice's server?
SourceHut has reminded GitHub users that Git has always had this (for most) arcane
git send-emailcommand that is the original way to send patches, using an once-open protocol.Turns out Nostr acts as a quite powerful email replacement and can be used to send text content just like email, therefore patches are a very good fit for Nostr event contents.
Once you get used to it and the proper UIs (or CLIs) are built sending and applying patches to and from others becomes a much easier flow than the intense clickops mixed with terminal copypasting that is interacting with GitHub (you have to clone the repository on GitHub, then update the remote URL in your local directory, then create a branch and then go back and turn that branch into a Pull Request, it's quite tiresome) that many people already dislike so much they went out of their way to build many GitHub CLI tools just so they could comment on issues and approve pull requests from their terminal.
Replacing GitHub features
Aside from being the "hub" that people use to send patches to other people's code (because no one can do the email flow anymore, justifiably), GitHub also has 3 other big features that are not directly related to Git, but that make its network-effect harder to overcome. Luckily Nostr can be used to create a new environment in which these same features are implemented in a more decentralized and healthy way.
Issues: bug reports, feature requests and general discussions
Since the "Issues" GitHub feature is just a bunch of text comments it should be very obvious that Nostr is a perfect fit for it.
I will not even mention the fact that Nostr is much better at threading comments than GitHub (which doesn't do it at all), which can generate much more productive and organized discussions (and you can opt out if you want).
Search
I use GitHub search all the time to find libraries and projects that may do something that I need, and it returns good results almost always. So if people migrated out to other code hosting providers wouldn't we lose it?
The fact is that even though we think everybody is on GitHub that is a globalist falsehood. Some projects are not on GitHub, and if we use only GitHub for search those will be missed. So even if we didn't have a Nostr Git alternative it would still be necessary to create a search engine that incorporated GitLab, Codeberg, SourceHut and whatnot.
Turns out on Nostr we can make that quite easy by not forcing anyone to integrate custom APIs or hardcoding Git provider URLs: each repository can make itself available by publishing an "announcement" event with a brief description and one or more Git URLs. That makes it easy for a search engine to index them -- and even automatically download the code and index the code (or index just README files or whatever) without a centralized platform ever having to be involved.
The relays where such announcements will be available play a role, of course, but that isn't a bad role: each announcement can be in multiple relays known for storing "public good" projects, some relays may curate only projects known to be very good according to some standards, other relays may allow any kind of garbage, which wouldn't make them good for a search engine to rely upon, but would still be useful in case one knows the exact thing (and from whom) they're searching for (the same is valid for all Nostr content, by the way, and that's where it's censorship-resistance comes from).
Continuous integration
GitHub Actions are a very hardly subsidized free-compute-for-all-paid-by-Microsoft feature, but one that isn't hard to replace at all. In fact there exists today many companies offering the same kind of service out there -- although they are mostly targeting businesses and not open-source projects, before GitHub Actions was introduced there were also many that were heavily used by open-source projects.
One problem is that these services are still heavily tied to GitHub today, they require a GitHub login, sometimes BitBucket and GitLab and whatnot, and do not allow one to paste an arbitrary Git server URL, but that isn't a thing that is very hard to change anyway, or to start from scratch. All we need are services that offer the CI/CD flows, perhaps using the same framework of GitHub Actions (although I would prefer to not use that messy garbage), and charge some few satoshis for it.
It may be the case that all the current services only support the big Git hosting platforms because they rely on their proprietary APIs, most notably the webhooks dispatched when a repository is updated, to trigger the jobs. It doesn't have to be said that Nostr can also solve that problem very easily.
-
 @ 6e64b83c:94102ee8
2025-04-23 20:23:34
@ 6e64b83c:94102ee8
2025-04-23 20:23:34How to Run Your Own Nostr Relay on Android with Cloudflare Domain
Prerequisites
- Install Citrine on your Android device:
- Visit https://github.com/greenart7c3/Citrine/releases
- Download the latest release using:
- zap.store
- Obtainium
- F-Droid
- Or download the APK directly
-
Note: You may need to enable "Install from Unknown Sources" in your Android settings
-
Domain Requirements:
- Purchase a domain if you don't have one
-
Transfer your domain to Cloudflare if it's not already there (for free SSL certificates and cloudflared support)
-
Tools to use:
- nak (the nostr army knife):
- Download from https://github.com/fiatjaf/nak/releases
- Installation steps:
-
For Linux/macOS: ```bash # Download the appropriate version for your system wget https://github.com/fiatjaf/nak/releases/latest/download/nak-linux-amd64 # for Linux # or wget https://github.com/fiatjaf/nak/releases/latest/download/nak-darwin-amd64 # for macOS
# Make it executable chmod +x nak-*
# Move to a directory in your PATH sudo mv nak-* /usr/local/bin/nak
- For Windows:batch # Download the Windows version curl -L -o nak.exe https://github.com/fiatjaf/nak/releases/latest/download/nak-windows-amd64.exe# Move to a directory in your PATH (e.g., C:\Windows) move nak.exe C:\Windows\nak.exe
- Verify installation:bash nak --version ```
Setting Up Citrine
- Open the Citrine app
- Start the server
- You'll see it running on
ws://127.0.0.1:4869(local network only) - Go to settings and paste your npub into "Accept events signed by" inbox and press the + button. This prevents others from publishing events to your personal relay.
Installing Required Tools
- Install Termux from Google Play Store
- Open Termux and run:
bash pkg update && pkg install wget wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-arm64.deb dpkg -i cloudflared-linux-arm64.debCloudflare Authentication
- Run the authentication command:
bash cloudflared tunnel login - Follow the instructions:
- Copy the provided URL to your browser
- Log in to your Cloudflare account
- If the URL expires, copy it again after logging in
Creating the Tunnel
- Create a new tunnel:
bash cloudflared tunnel create <TUNNEL_NAME> - Choose any name you prefer for your tunnel
-
Copy the tunnel ID after creating the tunnel
-
Create and configure the tunnel config:
bash touch ~/.cloudflared/config.yml nano ~/.cloudflared/config.yml -
Add this configuration (replace the placeholders with your values): ```yaml tunnel:
credentials-file: /data/data/com.termux/files/home/.cloudflared/ .json ingress: - hostname: nostr.yourdomain.com service: ws://localhost:4869
- service: http_status:404 ```
- Note: In nano editor:
CTRL+Oand Enter to saveCTRL+Xto exit
-
Note: Check the credentials file path in the logs
-
Validate your configuration:
bash cloudflared tunnel validate -
Start the tunnel:
bash cloudflared tunnel run my-relay
Preventing Android from Killing the Tunnel
Run these commands to maintain tunnel stability:
bash date && apt install termux-tools && termux-setup-storage && termux-wake-lock echo "nameserver 1.1.1.1" > $PREFIX/etc/resolv.confTip: You can open multiple Termux sessions by swiping from the left edge of the screen while keeping your tunnel process running.
Updating Your Outbox Model Relays
Once your relay is running and accessible via your domain, you'll want to update your relay list in the Nostr network. This ensures other clients know about your relay and can connect to it.
Decoding npub (Public Key)
Private keys (nsec) and public keys (npub) are encoded in bech32 format, which includes: - A prefix (like nsec1, npub1 etc.) - The encoded data - A checksum
This format makes keys: - Easy to distinguish - Hard to copy incorrectly
However, most tools require these keys in hexadecimal (hex) format.
To decode an npub string to its hex format:
bash nak decode nostr:npub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4Change it with your own npub.
bash { "pubkey": "6e64b83c1f674fb00a5f19816c297b6414bf67f015894e04dd4c657e94102ee8" }Copy the pubkey value in quotes.
Create a kind 10002 event with your relay list:
- Include your new relay with write permissions
- Include other relays you want to read from and write to, omit 3rd parameter to make it both read and write
Example format:
json { "kind": 10002, "tags": [ ["r", "wss://your-relay-domain.com", "write"], ["r", "wss://eden.nostr.land/"], ["r", "wss://nos.lol/"], ["r", "wss://nostr.bitcoiner.social/"], ["r", "wss://nostr.mom/"], ["r", "wss://relay.primal.net/"], ["r", "wss://nostr.wine/", "read"], ["r", "wss://relay.damus.io/"], ["r", "wss://relay.nostr.band/"], ["r", "wss://relay.snort.social/"] ], "content": "" }Save it to a file called
event.jsonNote: Add or remove any relays you want. To check your existing 10002 relays: - Visit https://nostr.band/?q=by%3Anpub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4+++kind%3A10002 - nostr.band is an indexing service, it probably has your relay list. - Replace
npub1xxxin the URL with your own npub - Click "VIEW JSON" from the menu to see the raw event - Or use thenaktool if you know the relaysbash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.comReplace `<your-pubkey>` with your public key in hex format (you can get it using `nak decode <your-npub>`)- Sign and publish the event:
- Use a Nostr client that supports kind 10002 events
- Or use the
nakcommand-line tool:bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)
Important Security Notes: 1. Never share your nsec (private key) with anyone 2. Consider using NIP-49 encrypted keys for better security 3. Never paste your nsec or private key into the terminal. The command will be saved in your shell history, exposing your private key. To clear the command history: - For bash: use
history -c- For zsh: usefc -Wto write history to file, thenfc -pto read it back - Or manually edit your shell history file (e.g.,~/.zsh_historyor~/.bash_history) 4. if you're usingzsh, usefc -pto prevent the next command from being saved to history 5. Or temporarily disable history before running sensitive commands:bash unset HISTFILE nak key encrypt ... set HISTFILEHow to securely create NIP-49 encypted private key
```bash
Read your private key (input will be hidden)
read -s SECRET
Read your password (input will be hidden)
read -s PASSWORD
encrypt command
echo "$SECRET" | nak key encrypt "$PASSWORD"
copy and paste the ncryptsec1 text from the output
read -s ENCRYPTED nak key decrypt "$ENCRYPTED"
clear variables from memory
unset SECRET PASSWORD ENCRYPTED ```
On a Windows command line, to read from stdin and use the variables in
nakcommands, you can use a combination ofset /pto read input and then use those variables in your command. Here's an example:```bash @echo off set /p "SECRET=Enter your secret key: " set /p "PASSWORD=Enter your password: "
echo %SECRET%| nak key encrypt %PASSWORD%
:: Clear the sensitive variables set "SECRET=" set "PASSWORD=" ```
If your key starts with
ncryptsec1, thenaktool will securely prompt you for a password when using the--secparameter, unless the command is used with a pipe< >or|.bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)- Verify the event was published:
- Check if your relay list is visible on other relays
-
Use the
naktool to fetch your kind 10002 events:bash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.com -
Testing your relay:
- Try connecting to your relay using different Nostr clients
- Verify you can both read from and write to your relay
- Check if events are being properly stored and retrieved
- Tip: Use multiple Nostr clients to test different aspects of your relay
Note: If anyone in the community has a more efficient method of doing things like updating outbox relays, please share your insights in the comments. Your expertise would be greatly appreciated!
-
 @ 3a8a16a7:f4c3b0b4
2025-04-29 22:48:07
@ 3a8a16a7:f4c3b0b4
2025-04-29 22:48:07test
-
 @ 3c389c8f:7a2eff7f
2025-04-29 18:07:00
@ 3c389c8f:7a2eff7f
2025-04-29 18:07:00Extentions:
https://chromewebstore.google.com/detail/flamingo-%E2%80%93-nostr-extensio/alkiaengfedemppafkallgifcmkldohe
https://chromewebstore.google.com/detail/nos2x/kpgefcfmnafjgpblomihpgmejjdanjjp
https://chromewebstore.google.com/detail/aka-profiles/ncmflpbbagcnakkolfpcpogheckolnad
https://keys.band/
https://github.com/haorendashu/nowser
The Remote Signer:
https://nsec.app/
https://github.com/kind-0/nsecbunkerd
Native Android Signer:
https://github.com/greenart7c3/amber
iOS
https://testflight.apple.com/join/8TFMZbMs
https://testflight.apple.com/join/DUzVMDMK
Higher Security Options: To start using Nostr with a secure, recoverable keypair: https://nstart.me/en
For Existing Keys: https://www.frostr.org/
Thank you to https://nostr.net/ for keeping a thorough list of Nostr apps, clients, and tools!
-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ 266815e0:6cd408a5
2025-04-29 17:47:57
@ 266815e0:6cd408a5
2025-04-29 17:47:57I'm excited to announce the release of Applesauce v1.0.0! There are a few breaking changes and a lot of improvements and new features across all packages. Each package has been updated to 1.0.0, marking a stable API for developers to build upon.
Applesauce core changes
There was a change in the
applesauce-corepackage in theQueryStore.The
Queryinterface has been converted to a method instead of an object withkeyandrunfields.A bunch of new helper methods and queries were added, checkout the changelog for a full list.
Applesauce Relay
There is a new
applesauce-relaypackage that provides a simple RxJS based api for connecting to relays and publishing events.Documentation: applesauce-relay
Features:
- A simple API for subscribing or publishing to a single relay or a group of relays
- No
connectorclosemethods, connections are managed automatically by rxjs - NIP-11
auth_requiredsupport - Support for NIP-42 authentication
- Prebuilt or custom re-connection back-off
- Keep-alive timeout (default 30s)
- Client-side Negentropy sync support
Example Usage: Single relay
```typescript import { Relay } from "applesauce-relay";
// Connect to a relay const relay = new Relay("wss://relay.example.com");
// Create a REQ and subscribe to it relay .req({ kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events"); } else { console.log("Received event:", response); } }); ```
Example Usage: Relay pool
```typescript import { Relay, RelayPool } from "applesauce-relay";
// Create a pool with a custom relay const pool = new RelayPool();
// Create a REQ and subscribe to it pool .req(["wss://relay.damus.io", "wss://relay.snort.social"], { kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events on all relays"); } else { console.log("Received event:", response); } }); ```
Applesauce actions
Another new package is the
applesauce-actionspackage. This package provides a set of async operations for common Nostr actions.Actions are run against the events in the
EventStoreand use theEventFactoryto create new events to publish.Documentation: applesauce-actions
Example Usage:
```typescript import { ActionHub } from "applesauce-actions";
// An EventStore and EventFactory are required to use the ActionHub import { eventStore } from "./stores.ts"; import { eventFactory } from "./factories.ts";
// Custom publish logic const publish = async (event: NostrEvent) => { console.log("Publishing", event); await app.relayPool.publish(event, app.defaultRelays); };
// The
publishmethod is optional for the asyncrunmethod to work const hub = new ActionHub(eventStore, eventFactory, publish); ```Once an
ActionsHubis created, you can use therunorexecmethods to execute actions:```typescript import { FollowUser, MuteUser } from "applesauce-actions/actions";
// Follow fiatjaf await hub.run( FollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", );
// Or use the
execmethod with a custom publish method await hub .exec( MuteUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", ) .forEach((event) => { // NOTE: Don't publish this event because we never want to mute fiatjaf // pool.publish(['wss://pyramid.fiatjaf.com/'], event) }); ```There are a log more actions including some for working with NIP-51 lists (private and public), you can find them in the reference
Applesauce loaders
The
applesauce-loaderspackage has been updated to support any relay connection libraries and not justrx-nostr.Before:
```typescript import { ReplaceableLoader } from "applesauce-loaders"; import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(rxNostr); ```
After:
```typescript
import { Observable } from "rxjs"; import { ReplaceableLoader, NostrRequest } from "applesauce-loaders"; import { SimplePool } from "nostr-tools";
// Create a new nostr-tools pool const pool = new SimplePool();
// Create a method that subscribes using nostr-tools and returns an observable function nostrRequest: NostrRequest = (relays, filters, id) => { return new Observable((subscriber) => { const sub = pool.subscribe(relays, filters, { onevent: (event) => { subscriber.next(event); }, onclose: () => subscriber.complete(), oneose: () => subscriber.complete(), });
return () => sub.close();}); };
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
Of course you can still use rx-nostr if you want:
```typescript import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a method that subscribes using rx-nostr and returns an observable function nostrRequest( relays: string[], filters: Filter[], id?: string, ): Observable
{ // Create a new oneshot request so it will complete when EOSE is received const req = createRxOneshotReq({ filters, rxReqId: id }); return rxNostr .use(req, { on: { relays } }) .pipe(map((packet) => packet.event)); } // Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
There where a few more changes, check out the changelog
Applesauce wallet
Its far from complete, but there is a new
applesauce-walletpackage that provides a actions and queries for working with NIP-60 wallets.Documentation: applesauce-wallet
Example Usage:
```typescript import { CreateWallet, UnlockWallet } from "applesauce-wallet/actions";
// Create a new NIP-60 wallet await hub.run(CreateWallet, ["wss://mint.example.com"], privateKey);
// Unlock wallet and associated tokens/history await hub.run(UnlockWallet, { tokens: true, history: true }); ```
-
 @ 3ffac3a6:2d656657
2025-04-15 14:49:31
@ 3ffac3a6:2d656657
2025-04-15 14:49:31🏅 Como Criar um Badge Épico no Nostr com
nak+ badges.pageRequisitos:
- Ter o
nakinstalado (https://github.com/fiatjaf/nak) - Ter uma chave privada Nostr (
nsec...) - Acesso ao site https://badges.page
- Um relay ativo (ex:
wss://relay.primal.net)
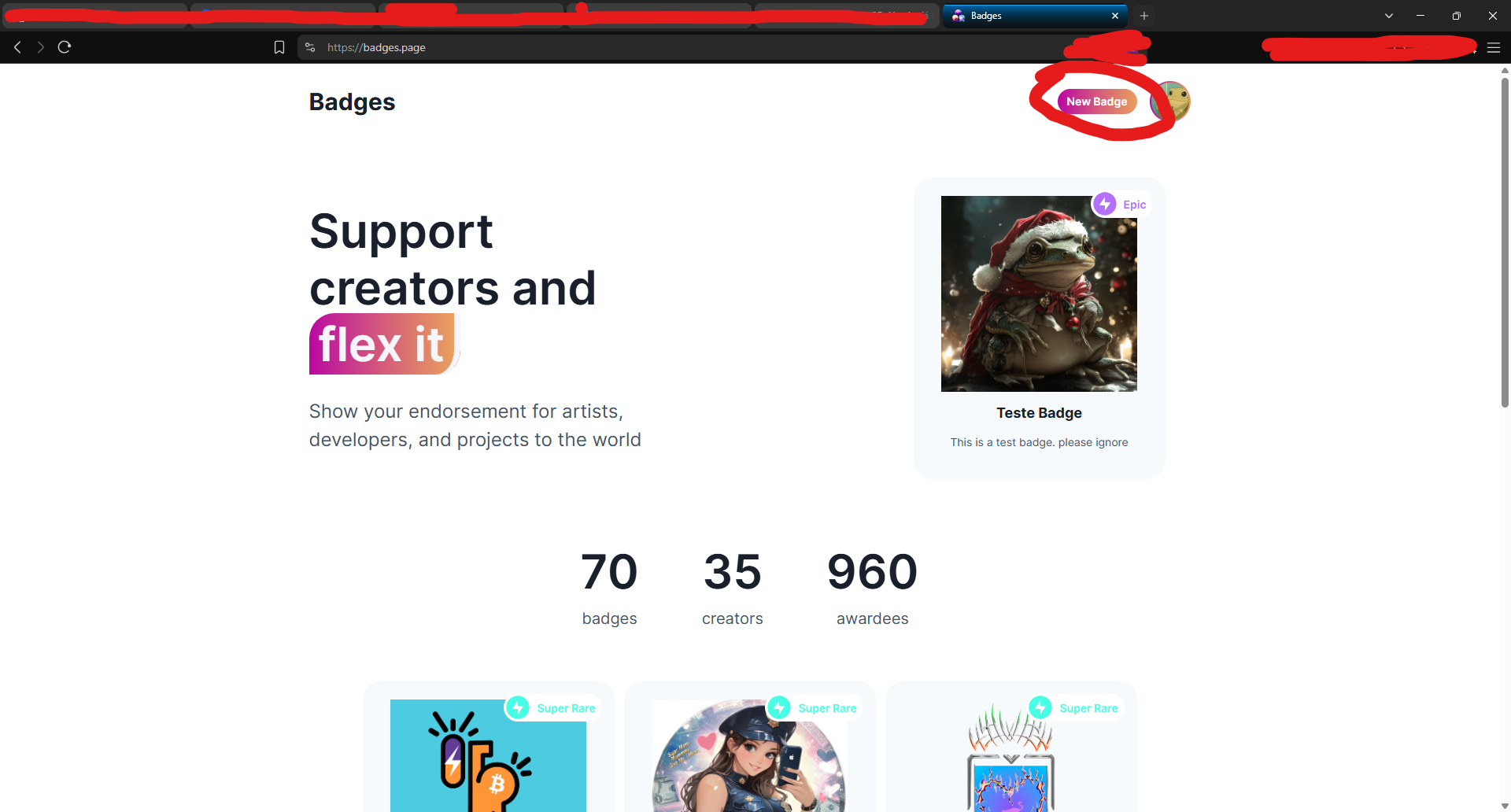
🔧 Passo 1 — Criar o badge em badges.page
- Acesse o site https://badges.page
-
Clique em "New Badge" no canto superior direito
-
Preencha os campos:
- Nome (ex:
Teste Épico) - Descrição
-
Imagem e thumbnail
-
Após criar, você será redirecionado para a página do badge.
🔍 Passo 2 — Copiar o
naddrdo badgeNa barra de endereços, copie o identificador que aparece após
/a/— este é o naddr do seu badge.Exemplo:
nostr:naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Copie:
naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0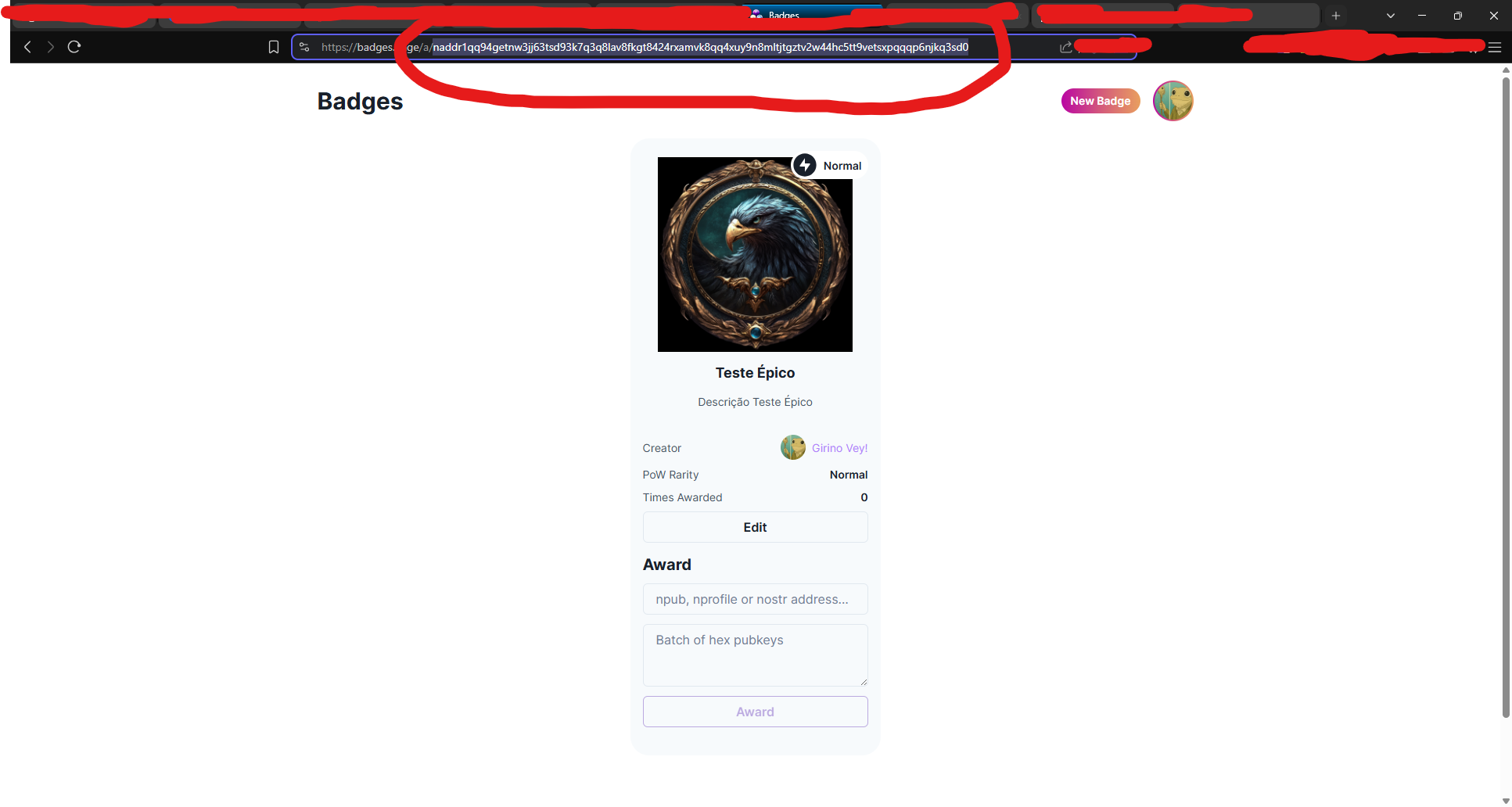
🧠 Passo 3 — Decodificar o naddr com
nakAbra seu terminal (ou Cygwin no Windows) e rode:
bash nak decode naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Você verá algo assim:
json { "pubkey": "3ffac3a6c859eaaa8cdddb2c7002a6e10b33efeb92d025b14ead6f8a2d656657", "kind": 30009, "identifier": "Teste-Epico" }Grave o campo
"identifier"— nesse caso: Teste-Epico
🛰️ Passo 4 — Consultar o evento no relay
Agora vamos pegar o evento do badge no relay:
bash nak req -d "Teste-Epico" wss://relay.primal.netVocê verá o conteúdo completo do evento do badge, algo assim:
json { "kind": 30009, "tags": [["d", "Teste-Epico"], ["name", "Teste Épico"], ...] }
💥 Passo 5 — Minerar o evento como "épico" (PoW 31)
Agora vem a mágica: minerar com proof-of-work (PoW 31) para que o badge seja classificado como épico!
bash nak req -d "Teste-Epico" wss://relay.primal.net | nak event --pow 31 --sec nsec1SEU_NSEC_AQUI wss://relay.primal.net wss://nos.lol wss://relay.damus.ioEsse comando: - Resgata o evento original - Gera um novo com PoW de dificuldade 31 - Assina com sua chave privada
nsec- E publica nos relays wss://relay.primal.net, wss://nos.lol e wss://relay.damus.io⚠️ Substitua
nsec1SEU_NSEC_AQUIpela sua chave privada Nostr.
✅ Resultado
Se tudo der certo, o badge será atualizado com um evento de PoW mais alto e aparecerá como "Epic" no site!
- Ter o
-
 @ fd06f542:8d6d54cd
2025-04-28 05:52:48
@ fd06f542:8d6d54cd
2025-04-28 05:52:48什么是narr?
今天翻 fiatjaf 仓库 竟然发现了这个宝贝 narr和我最进做的 nostrbook.com有交集。
? 交集在哪里呢? narr (not another rss reader) is a web-based RSS and Nostr long-form feed aggregator which can be used both as a desktop application and a personal self-hosted server. 1. long-form ,也就是30023. 2. desktop application
这两点足够对我有吸引力。
下载,运行 界面不错。 继续!
 {.user-img}
{.user-img}不过这个是需要 自己通过浏览器浏览的。并没有独立打包成一个app。那么问题来了,不够阿。
顺着他的介绍,The app is a single binary with an embedded database (SQLite), it is based on yarr.
yarr
我去看了看yarr 是可支持gui的,不过Linux支持的不够,我平时基本就是Linux。 怎么办?
webkit
用webkit套一个吧。 ```go package main
/*
cgo linux pkg-config: webkit2gtk-4.1 gtk+-3.0
include
include
static void initAndShow(GtkWidget *window, const char url) { // 必须初始化 GTK gtk_init(NULL, NULL);
*window = gtk_window_new(GTK_WINDOW_TOPLEVEL); gtk_window_set_title(GTK_WINDOW(*window), "nostrbook.com"); gtk_window_set_default_size(GTK_WINDOW(*window), 1024, 600); // 创建 WebView GtkWidget *webview = webkit_web_view_new(); gtk_container_add(GTK_CONTAINER(*window), webview); webkit_web_view_load_uri(WEBKIT_WEB_VIEW(webview), url); // 显示窗口 gtk_widget_show_all(*window);} */ import "C" import ( "unsafe" )
func main() { var window *C.GtkWidget url := C.CString("http://127.0.0.1:7049") defer C.free(unsafe.Pointer(url))
// 调用 C 函数初始化 C.initAndShow(&window, url) // 进入 GTK 主循环 C.gtk_main()}
```
什么是下一步呢?
继续研究吧,看看go + webkit 能不能打包 这个 http server ?
再看看 有没有可以编辑的 md ide 用simple 也可以的。
等等看吧。
-
 @ ec9bd746:df11a9d0
2025-03-07 20:13:38
@ ec9bd746:df11a9d0
2025-03-07 20:13:38I was diving into PoW (Proof-of-Work) once again after nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3wamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmny9uqzqj8a67jths8euy33v5yu6me6ngua5v3y3qq3dswuqh2pejmtls6datagmu rekindled my interest with his PoW Draw project. It was a fun little trifle, but it shifted my focus just the right way at the right time.
Because then, on Friday, came the Oval Office Travesty. Once I got over the initial shock, I decided I couldn't just curse and lament; I needed to do something bigger, something symbolic, something expressive. So that's exactly what I did—breaking nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqewrqnkx4zsaweutf739s0cu7et29zrntqs5elw70vlm8zudr3y2t9v7jg's record which he held for almost 2 and half years.
Here is a note with PoW 45, the highest PoW known to Nostr (as of now).
nostr:nevent1qvzqqqqqqypzpmym6ar92346qc04ml08z6j0yrelylkv9r9ysurhte0g2003r2wsqy88wumn8ghj7mn0wvhxcmmv9uqsuamnwvaz7tmwdaejumr0dshsqgqqqqqqqqqy8t8awr5c8z4yfp4cr8v7spp8psncv8twlh083flcr582fyu9
How Did I Pull It Off?
In theory, quite simple: Create note, run PoW mining script & wait.
Thanks to PoW Draw, I already had mining software at hand: nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqvqc5tlvn6etv09f0fvuauves49dvgnukjtzsndfv9y8yyrqyxmz7dty6z's notemine_hw, but when you know that there is a 1 in 2^45 chance that the next hash will be the correct one you want to increase the odds a bit. So on Monday evening, I started my Note Mining operation on an old 40 thread machine called Workhorse.
Issues Along the Way
I was immediately surprised that Workhorse (2× Intel Xeon Silver 4114) produced only about 3Mh/s. A laptop (Intel Core i7-1185G7) with Windows and all the bloat did 5Mh/s. That was strange.
Another hurdle was that notemine_hw does not refresh the
created_atfield. With just a few Mh/s of power I was potentially looking at weeks of computation, by then the note would be quite stale. So I created systemd service leveraging theRuntimeMaxSecoption to periodically restart every 3600 seconds assuring that the Note would be max 1 hour old at the time of publishing.Luckily PoW is that kind of problem where every hash attempt is an independent event, so the chance of success is the same whether you do it in small increments or one uninterrupted stretch. So by restarting the mining process I was only losing a few mere seconds every hour due to the overhead.
Once the note staleness issue was resolved, I looked at the 40 workers on Workhorse vs. 7 workers on the laptop and start messing around with running one instance with 40 workers and running 40 instances with 1 worker and found out, that the workers are not bound to a CPU thread and are jumping between the CPUs like rabbits high on Colombian carrots.
The solution? Running multiple instances with one worker each as a service locked to its own CPU core using systemd's
CPUAffinityoption. ``` $aida@workhorse:systemd/system $ sudo cat notemine@.service [Unit] Description=Notemine HW Publish (restarts hourly)[Service] Type=simple CPUAffinity=%i
The command to run:
ExecStart=/home/aida/.cargo/bin/notemine_hw publish --n-workers 1 --difficulty 45 --event-json /home/aida/note.json --relay-url 'wss://wot.shaving.kiwi' --nsec nsec0123456789abcdef
Let the process run for 1 hour (3600 seconds), then systemd will stop it:
RuntimeMaxSec=3600 TimeoutStopSec=1
Tells systemd to restart the service automatically after it stops:
Restart=always RestartSec=1
run as a non-root user:
User=aida Group=aida
[Install] WantedBy=multi-user.target ``` Then I added a starting service to spawn an instance for each CPU thread.
``` $aida@workhorse:systemd/system $ sudo cat notemine_start.service [Unit] Description=Start all services in sequence with 3-second intervals
[Service] Type=oneshot ExecStart=/usr/bin/zsh /home/aida/notemine_start.sh
RemainAfterExit=yes
[Install] WantedBy=multi-user.target
Here is the startup script (I know, loops exist—but Ctrl+C/Ctrl+V is so old-school):aida@workhorse:~ $ cat notemine_start.sh /usr/bin/systemctl start notemine@0.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@1.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@2.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@3.service /usr/bin/sleep 3 ... ... ... /usr/bin/systemctl start notemine@38.service`` The sleep there is critical to make sure that thecreated_at`timestamps are different, preventing redundant hashing.This adjustment made Workhorse the strongest machine in my fleet with 10+Mh/s.
The Luck Aspect
From Monday evening, I started adding all machines at my disposal into the fleet and by Wednesday evening I was crunching hashes on about 130 CPU threads (a lot of them were quite antique) and at the peak was just little shy of 40Mh/s. To compensate for the slow start with the few above-mentioned hiccups and the fact that I had to use my desktop to do other things from time to time, I counted with the conservative estimate of 30Mh/s when I was doing all the probability calculations.
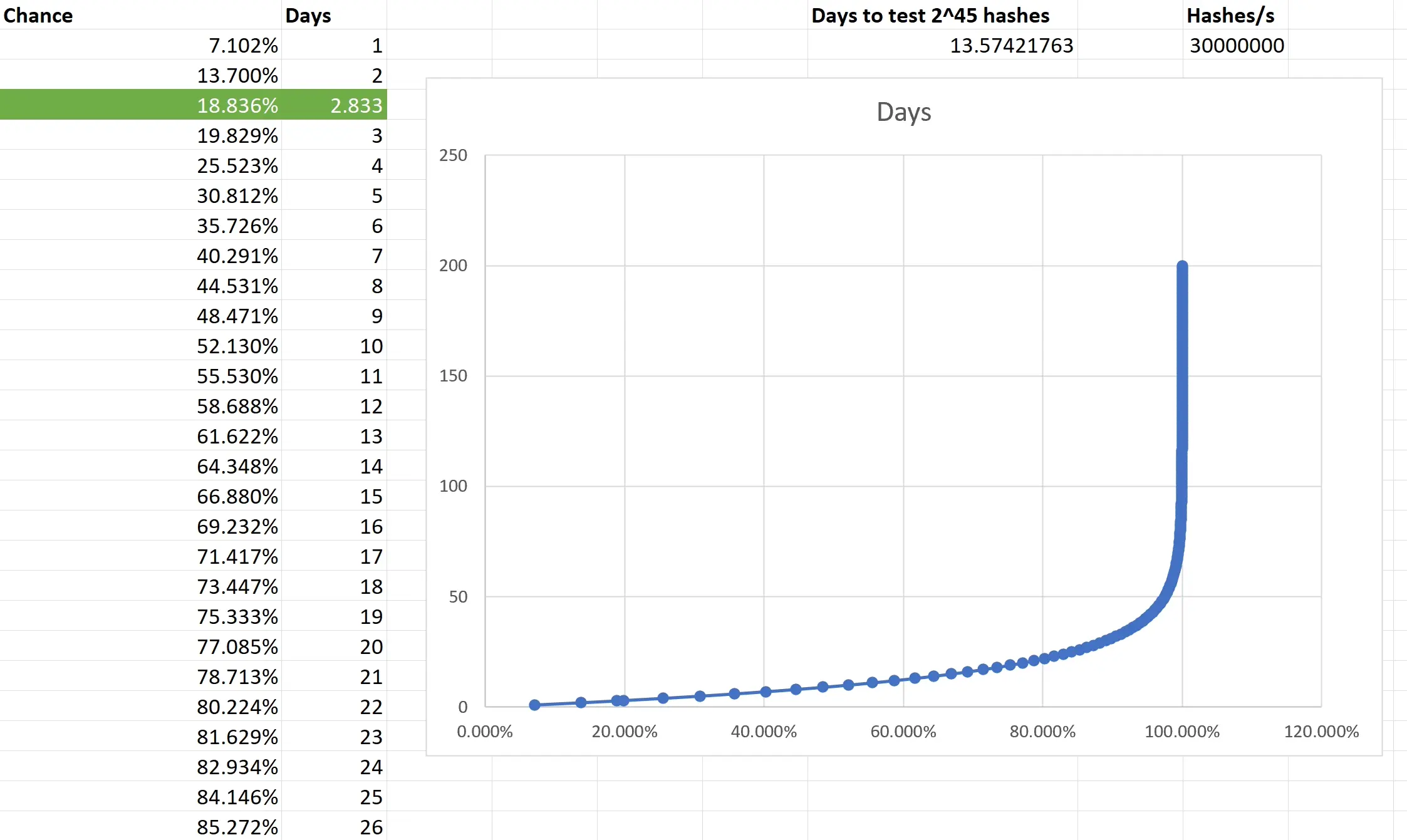
Based on the type of task that PoW mining is, the outcome is not predictible. You are only looking at what is the chance that the outcome of every single independent event will be consecutively non-favourable and then subtracting it from 1 to get the chance of that single favourable event you want. I really had to brush up on my combinatorics and discrete mathematics to make sure I have at least an elementary understanding of what is going on. Also, because we are not just throwing a dice 5 times, but are operating with big numbers, approximation was necessary. Luckily, the formula is available and quite simple in the end.
Two weeks to exhauste all the possible tries still doesn't guarantee anything, actually there is a slighlty less than 2 in 3 chance that you will have a result after all that time. So the fact that I was able to hit the right hash in less than 3 days was good luck. Not insane lottery winning luck, but good luck; slighlty lower than 1 in 5.
Do you want to beat me?
Go ahead! All the pitfalls are described above and until there is a GPU-based PoW Mining available, we are all on pretty even ground.
Do you hate the note?
In that case, feel free to enjoy this accompanying image:

-
 @ c582af78:698069cc
2025-02-15 19:21:25
@ c582af78:698069cc
2025-02-15 19:21:25The Face of God: How Art Became a Gateway to the Divine
If you live in the West, you’re surrounded by depictions of God, Jesus, and the saints—from paintings and statues to illustrated Bibles and stained glass windows.
But this is far from universal. In the Islamic world, religious art takes a very different form: vibrant colors, intricate geometry, and architectural symmetry. Depictions of God or Muhammad aren’t just discouraged—they are outright forbidden.
But why?
To answer that, we must go back to the origins of the Abrahamic religions—when early Christians, Jews, and Muslims were surprisingly unified in their views on religious art.
https://image.nostr.build/1515c5fd00d798cd283583618bbbc0d5eb91bc481a84c21d53644d42fa30173a.jpg
The Early Christian Hesitation
The first generation of Christians were deeply aware of Judaism’s strict prohibition against idol worship. Depicting God in any form was considered dangerous—a potential gateway to paganism.
For centuries, Christianity could have followed this path, rejecting religious imagery altogether. But one fundamental theological idea changed everything:
The Incarnation.
As the early Church wrestled with the nature of Christ, heated debates emerged:
- Was he part human and part divine?
- Was he fully human and fully divine?
- And what did the Gospel of John mean by “the Word became flesh and dwelt among us”?
The result of these debates was the doctrine of the Incarnation—the belief that God took on human form in real flesh and blood. And if God himself had chosen to be seen in finite form, then depicting Him in art could no longer be considered blasphemous.
This single theological shift laid the foundation for Christianity’s embrace of religious art—a decision that would not only shape Christian worship but redefine how we engage with art itself.
https://image.nostr.build/1cf9ea5d1385c46bd720de9c7de65123428a9f76356e39e37c5d7b9663993930.jpg
Let There Be Art…
How did this change Christian art?
https://image.nostr.build/b945e4ea06b281bb4618f08b2543108beecf7f510aaa795bed1c833614e32fb7.jpg
The early objections to religious imagery went something like this:
“God is infinite and mysterious. Reducing Him to a finite, limited form is blasphemy.”
But with the Incarnation, the argument flipped:
“If God took on real shape, color, and form without diminishing His divine nature, then we can depict Him in art without compromising His grandeur.”
Thus, images of Jesus, Mary, and saints not only became permissible—they were encouraged.
Christian leaders actively commissioned religious art to communicate the Gospel visually to a largely illiterate population. Paintings, statues, and stained glass became tools of evangelization, helping people grasp biblical stories without needing to read.
Take the Duomo of Milan with its 4,000 statues. They aren’t just decorative. They inspire faith by highlighting the lives of the saints.
Christianity had embraced art as a spiritual bridge, a way to connect the finite with the infinite.
https://image.nostr.build/4f6b79a9179d818a951bf461ee5ff785cbe618ed376b4a56d92e77dcb34005bc.jpg
The Criticism: Were They Worshiping the Art?
Not everyone agreed.
Some critics argued that Christians were focusing too much on the art itself, rather than the God it was meant to represent.
https://image.nostr.build/29afb401ef99d2b6c59b71d8534a5160c25d2ca468d81251ba0f55d033679490.jpg
But the Church’s response was clear:
"You are not meant to look at art, but through it.
Art is not the end goal—it is a gateway to something greater.
A painting of Christ isn’t meant to be worshiped—it’s meant to draw the viewer into His story, His sacrifice, and His message.
This perspective didn’t just shape religious art. It fundamentally changed how we experience all forms of art, even secular ones.
To Infinity and Beyond: The Lasting Impact of Religious Art
Christianity’s view of art—that it should point beyond itself—has so deeply influenced Western culture that we often don’t even realize it.
Think about how we experience books, music, and movies:
- A great novel inspires courage.
- A powerful song moves you to tears.
- A gripping film motivates you to keep going in life.
The best art doesn’t just exist for its own sake—it transports you beyond the canvas, the page, or the screen.
This idea mirrors the Incarnation itself: an infinite God becoming finite to guide us back to the infinite.
Tolkien, The Lord of the Rings, and the Incarnation of Art
A perfect example? J.R.R. Tolkien’s The Lord of the Rings.
Tolkien infused his story with themes of brotherhood, heroism, and sacrifice—all timeless, transcendental ideas. But instead of leaving them as abstract concepts, he "incarnated" them into words on a page—finite, tangible, and deeply relatable.
https://image.nostr.build/b120c4d7c7232cf226af65c33cb7fc494f495d50b8ad4593a58f3528fd0b71dc.jpg
His goal? To turn the reader’s heart back to the infinite by making them experience these ideals in a concrete way.
The same can be said for any truly great art.
It doesn’t exist for itself—it exists to move you, to inspire you, to challenge you.
And next time you step into a cathedral, gaze at a masterpiece, or listen to a symphony, remember:
You’re not supposed to simply look at the art around you—
You’re supposed to look beyond it, into eternity.
-
 @ c582af78:698069cc
2025-02-15 04:20:11
@ c582af78:698069cc
2025-02-15 04:20:111. The Battle of Cannae (216 BC) – Rome’s Darkest Hour, and Its Defining Moment
During the Second Punic War, Hannibal of Carthage faced a Roman army that outnumbered his forces 2-to-1. Instead of retreating, he met them head-on with a brilliant tactical maneuver. His army encircled and annihilated the Romans, slaughtering over 50,000 soldiers in a single day—one of the most devastating defeats in Roman history.
https://image.nostr.build/a2ccbcc267d3bc30d24d80873612ba70d8f69a00bdd6a90fc3682f91d87eb956.jpg
Any other nation would have surrendered. But Rome refused. Instead, it adapted, shifting to a war of attrition, avoiding direct confrontations, and gradually wearing down Hannibal’s forces.
Cannae became a paradox—it was Rome’s greatest defeat, yet it forged the Roman spirit of perseverance and relentless determination. Rome ultimately turned the tide, defeated Carthage, and emerged as the dominant power in the Mediterranean.
https://image.nostr.build/9c29ef6b6cebd916c105271927adaa5fe4e668a6078595390936cd7898464c31.jpg
Hannibal’s tactics at Cannae changed warfare forever. His use of battlefield deception and encirclement is still studied in military academies today, and no commander worth his salt is unfamiliar with Hannibal’s masterpiece at Cannae.
2. The Battle of Marathon (490 BC) – The Birth of Western Civilization
When King Darius I of Persia invaded Greece, he sought to crush Athens and expand Persian control. The Athenians, vastly outnumbered, faced what seemed like certain defeat. But instead of waiting for the Persians to march inland, they struck first.
Using superior tactics and their knowledge of the terrain, the Athenians routed the Persian army, sending them fleeing to their ships.
https://image.nostr.build/63c4bdba98f7a2a4ccb3e2a8edcd43596b595284245f3a3395a3c53f51124558.jpg
This stunning victory didn’t just preserve Greek independence—it safeguarded the nascent idea of democracy. Without it, the Golden Age of Greece—the era that produced Socrates, the Parthenon, and the foundations of Western philosophy and governance—might never have happened.
Marathon remains a symbol of strategy and courage overcoming overwhelming odds. Without it, the world might never have known Athenian democracy, Greek philosophy, or the cultural foundations of the West.
https://image.nostr.build/017a314c11238433545977e681801904b8b702e1b568ff6c9438e8577721a243.jpg
3. The Battle of Hastings (1066) – The Making of Modern England
In 1066, William of Normandy led his army across the English Channel to claim the throne of England. At the Battle of Hastings, he faced King Harold II’s Anglo-Saxon forces in a brutal fight that would decide the future of the island.
William’s forces employed innovative strategies, including a feigned retreat, which broke Harold’s defensive lines. Harold was killed, and with him, Anglo-Saxon rule in England.
https://image.nostr.build/110045a76be0577defc5d9b884e5d811235f1992941847ca8a1b1a7b80c9bf79.jpg
Hastings completely transformed England. The Normans introduced a new ruling elite, reshaped governance, and left an enduring mark on the English language. Old English fused with Norman French, laying the foundation for modern English.
Beyond language, the Norman conquest brought England closer to continental Europe, influencing its legal systems, architecture, and culture for centuries. Hastings wasn’t just a military victory—it was a cultural watershed that forever changed England and, by extension, the world.
https://image.nostr.build/2799f91505263370ffb3a899ea4c79a65894f56673b81a024b206e013f3e73a9.jpg
4. The Battle of Lepanto (1571) – Christendom Strikes Back
By the late 16th century, the Ottoman Empire had become a dominant naval power, threatening Christian trading colonies and the stability of Europe’s maritime trade routes.
In 1570, the Ottomans besieged the Venetian-held island of Cyprus. After an 11-month siege, the starving Venetian garrison surrendered under promises of safe passage—but the Ottomans betrayed them, imprisoned the soldiers, and flayed their commander alive.
In response, the Papal States, Spain, Venice, Genoa, and other Christian powers set aside their rivalries and formed the Holy League. In a climactic naval showdown, over 130,000 men engaged in a fierce battle that ultimately ended in a decisive Christian victory.
https://image.nostr.build/0f233ec50e817874e1e6711a1e035b436e206b032d8cac8b33a68230beb20e1b.jpg
Lepanto halted Ottoman expansion into the western Mediterranean and reestablished European control over crucial sea routes. Among the soldiers that day was Miguel de Cervantes, who was wounded and lost the use of his left arm. His experience shaped his literary masterpiece, Don Quixote, further embedding Lepanto’s legacy in European art and culture.
5. The Battle of Trafalgar (1805) – Britain Secures Global Supremacy
In 1805, Napoleon sought to break British naval dominance by uniting the French and Spanish fleets against Admiral Horatio Nelson. The Battle of Trafalgar would decide the fate of European power at sea.
Outnumbered, Nelson devised an unorthodox strategy, splitting his fleet into two perpendicular columns to punch through enemy lines. The result? A decisive British victory—22 enemy ships destroyed without a single British vessel lost.
Trafalgar didn’t just shatter Napoleon’s naval ambitions—it secured Britain’s command of the seas for over a century. This naval dominance paved the way for the Pax Britannica, allowing Britain to expand its empire and maintain global influence well into the 20th century.
https://image.nostr.build/bf5e00f020a0755ea50c1bf1def870cfb226cb5ad18a91445eddac8389b2f05f.jpg
But Trafalgar’s legacy is also bittersweet—Nelson was fatally shot in battle. As he lay dying, he was informed of the victory. His last words?
“Now I am satisfied. Thank God, I have done my duty.”
Nelson’s death turned him into a national hero, and Trafalgar became a defining moment in British history.
More Than Just Battles
These five battles weren’t just clashes of armies—they were turning points that shaped the world.
- Cannae forged Rome’s resilience.
- Marathon preserved Greek democracy.
- Hastings reshaped England’s culture and language.
- Lepanto altered the balance of power in the Mediterranean.
- Trafalgar secured British naval dominance for a century.
Each of these battles reshaped civilizations—proving that history isn’t just written in words, but also in blood, steel, and strategy.
-
 @ dd1f9d50:06113a21
2025-02-05 01:48:55
@ dd1f9d50:06113a21
2025-02-05 01:48:55(Because Most People Don’t Understand Money)
The requisite knowledge needed to know whether $100 or $100,000 per Bitcoin is relatively speaking “a lot,” is what value means. One way to measure value is through a universal yardstick we call “Money.” The question of “What is money?” is perhaps one of the most overlooked and under answered in our day and age. There is even an entire podcast dedicated to that question with the eponymous title, hosted by Robert Breedlove. That podcast often delves into the more philosophical underpinnings whereas I hope to approach this with a more practical answer.
Money is a technology.
Money is the technology with which we interact with one another to reorganize goods and services to the place and time they are best suited. Most money of the past has been tangible (though not a requisite feature), scarce, recognizable (read: verifiable), durable, portable, and divisible. These features one might call the “Attributes of Money.” These attributes are absolutely essential for a money to maintain its status as a money. (Those of you who understand the U.S. Dollar system maybe scratching your heads right now but, believe me, I will address that elephant in due time.) These attributes, you may notice, are not a yes or no but more of a gradient. A money can be MORE portable than another yet, less durable. One more divisible but not scarce whatsoever. The point being they must have, in some capacity, these attributes or they simply aren’t money.
One of These Things is Not Like the Other
| | Bitcoin | Gold | Dollars | |-----------------|:----------------------------------------------------------------------------------------------------------------:|:------------------------------------------------------------------:|:--------------------------------------------------------------------------------------------------------------------------------------------------:| | Scarcity | 21 million coins
is the maximum supply | Unknown- the
supply grows roughly 2% per year | Also unknown to anyone outside of the Federal Reserve, Trillions and counting | | Recognizability | Each coin is verifiable to it's genesis on the timechain | Each molecule of gold has distinct physical verifiable properties | If the Federal reserve says it is a valid note, it is (Unless you are an enemy of the United States) | | Durablility | Each "Bitcoin" is information stored on a globally distributed network | Doesn't Rust and as far as can be measured Au197 is stable forever | Can be destroyed by any means that effect fabric and centralized databases | | Portability | Available wherever data can be store- Anywhere | Can be moved at 9.81 Newtons per Kilogram- Methods may vary | Can be moved physically with fabric notes- Digitally with express permission from a US accredited banking institution | | Divisibility | Currently can be divided into 100 million parts called Sats (can be further subdivided by adding decimal places) | Can be divided to the Atomic level (Though not practical) | Can be divided (without dilution) by adding new denominative bills or coinage
Can be divided (with dilution) by printing new bills or coinage | | | Bitcoin | Gold | Dollars |You may think with all of the great functionality of Bitcoin that the phrase "One of these things is not like the other" refers to BTC. No, I was referring to the Dollar. It is the only one on the list that was a currency that was substituted as some kind of faux money. It asserts itself, or rather the Federal Reserve asserts it, as money, de facto.
Dollars are NOT money.
Dollars are (allegedly) a currency. If money is a specific technology, currency is the financial infrastructure that allows that technology to reach and be used by the most number of people possible. This requires a firm tether between the asset being used as money and the currency used as a claim to that money. For example: If I hand you a chicken, you have a chicken. But, if I hand you a coupon that is redeemable for a chicken, you do not have a chicken. You have a claim to a chicken that is only as good as the party making that claim. Bringing it back to money again, dollars (Prior to 1971) were redeemable for gold at a rate of $35 per ounce. This is that strong tether that pegged dollars to gold and physical reality itself. Without a proof of work, mining, . Until…
WTF Happened in 1971?
The Nixon shock happened. Briefly, The U.S. took in Europe’s gold in the 1940’s to keep it out of Hitler’s hands. The U.S. made an agreement to peg the dollar to Europe’s gold. The U.S. over printed dollars in relation to the gold holdings. Around 1971 France (among others) called the U.S. out for devaluing the dollar and thus European currencies. So, Nixon “Temporarily” suspended the convertibility of dollars to gold. Now, here we all are like Wile E. Coyote having run off of the golden cliff clutching our dollars in our arms and 54 years later we still haven’t looked down to see the truth.
Dollars Aren’t Backed by Anything
This is why no country in the world today has a money standard. Seemingly they all forgot the number one rule of issuing currency, it must be backed by something. Now, you may hear dollar proponents say “The U.S. dollar is backed by the full faith and credit of the United States!” Another way of saying that is, “We said it is worth something, so it is!” This fiat (by decree) mentality creates a plethora of perverse incentives. The ever growing supply disallows users of the Dollar to save without inccuring the penalties of inflation.
Just a Few Examples of How You're Being Crushed
Because your dollar loses value:
- It pushes people to spend them on assets that seem to appreciate (as the dollar debases) but are truly staying stagnant.
- It pushes people to gamble on securities hoping the perceived value is enough to beat the inflationary curve.
- It pushes people away from saving for their future and the future of their families.
- It creates insane credit incentives so that people borrow way more than they can afford today knowing that dollars will be cheaper in the future. (Effectively a short position)
- It pushes people to spend less and less time making and maintaining their families as it becomes more expensive to keep a similar lifestyle to which it was founded.
These are just a few of the terrible consequences of not knowing that trading a currency with no monetary backing has on a society. Most may blame this soley on the ability to print currency by a central bank but, that is not the only factor. If the fed printed dollars against gold, people would simply take the best rate they could get and remonetize themselves with the gold. But because there is no monetary escape hatch guaranteed by the issuance of dollars, I.E. no one has to take your dollars in exchange for their Bitcoin or gold, you are left at the mercy of the market.
One Day, People Will Stop Accepting Your Dollars
Those lementing the high price of Bitcoin might want to thank their lucky stars that Bitcoin still has a rational number next to the "BTC 1=$?" sign. One day you will have to exchange something of actual value to the spender (no longer a seller). Your product, good or service, will be the only thing that anyone might be willing to part with their Bitcoin over. That is what makes a money, the most salable non-consumable good, whose only funtion is to back a financial structure that facilitates trade.
Bitcoin is Capital
Capital is a broad term that can describe anything that confers value or benefit to its owners, such as a factory and its machinery, or the financial assets of a business or an individual. Bitcoin being the latter creates the financial structures from which you build upon. You use capital to hold, transfer, and grow value. You do not do this with cash. Cash is a depreciating asset when you don't use it to gain goods or services for yourself or your business. This misconception around the equivalance between cash and money (financial capital) is what tricks people into believing Dollars are money. And what's worse is that even some of our greatest heroes have done this.
Slay Your Heroes, Within Reason
Unfortunately due to a mixing of verbiage that have very distinct differences, the title: "Bitcoin: A Peer-to-Peer Electronic Cash System" is technically inaccurate. Bitcoin doesn't fit the definition of cash, which is a liquid asset that can be easily converted into its equivalent value. In short, Satoshi misspoke. In reality, owning Bitcoin UTXOs (with private keys) means you already possess the asset, not just a claim to it. When you spend Bitcoin, the recipient receives the actual asset, not a promise of it. When you receive Bitcoin, you have final settlement on that transaction. Fundamentally Bitcoin is not cash, electronic or otherwise.
Bitcoin is Money.
-
 @ 3ffac3a6:2d656657
2025-02-04 04:31:26
@ 3ffac3a6:2d656657
2025-02-04 04:31:26In the waning days of the 20th century, a woman named Annabelle Nolan was born into an unremarkable world, though she herself was anything but ordinary. A prodigy in cryptography and quantum computing, she would later adopt the pseudonym Satoshi Nakamoto, orchestrating the creation of Bitcoin in the early 21st century. But her legacy would stretch far beyond the blockchain.
Annabelle's obsession with cryptography was not just about securing data—it was about securing freedom. Her work in quantum computing inadvertently triggered a cascade of temporal anomalies, one of which ensnared her in 2011. The event was cataclysmic yet silent, unnoticed by the world she'd transformed. In an instant, she was torn from her era and thrust violently back into the 16th century.
Disoriented and stripped of her futuristic tools, Annabelle faced a brutal reality: survive in a world where her knowledge was both a curse and a weapon. Reinventing herself as Anne Boleyn, she navigated the treacherous courts of Tudor England with the same strategic brilliance she'd used to design Bitcoin. Her intellect dazzled King Henry VIII, but it was the mysterious necklace she wore—adorned with a bold, stylized "B"—that fueled whispers. It was more than jewelry; it was a relic of a forgotten future, a silent beacon for any historian clever enough to decode her true story.
Anne's fate seemed sealed as she ascended to queenship, her influence growing alongside her enemies. Yet beneath the royal intrigue, she harbored a desperate hope: that the symbol around her neck would outlast her, sparking curiosity in minds centuries away. The "B" was her signature, a cryptographic clue embedded in history.
On the scaffold in 1536, as she faced her execution, Anne Boleyn's gaze was unwavering. She knew her death was not the end. Somewhere, in dusty archives and encrypted ledgers, her mark endured. Historians would puzzle over the enigmatic "B," and perhaps one day, someone would connect the dots between a queen, a coin, and a time anomaly born from quantum code.
She wasn't just Anne Boleyn. She was Satoshi Nakamoto, the time-displaced architect of a decentralized future, hiding in plain sight within the annals of history.
-
 @ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33
@ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33After my first major review of Primal on Android, we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client.
Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity.
It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub.
If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings.
Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in NIP-55. Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber.
This review of Amber is current as of version 3.2.5.
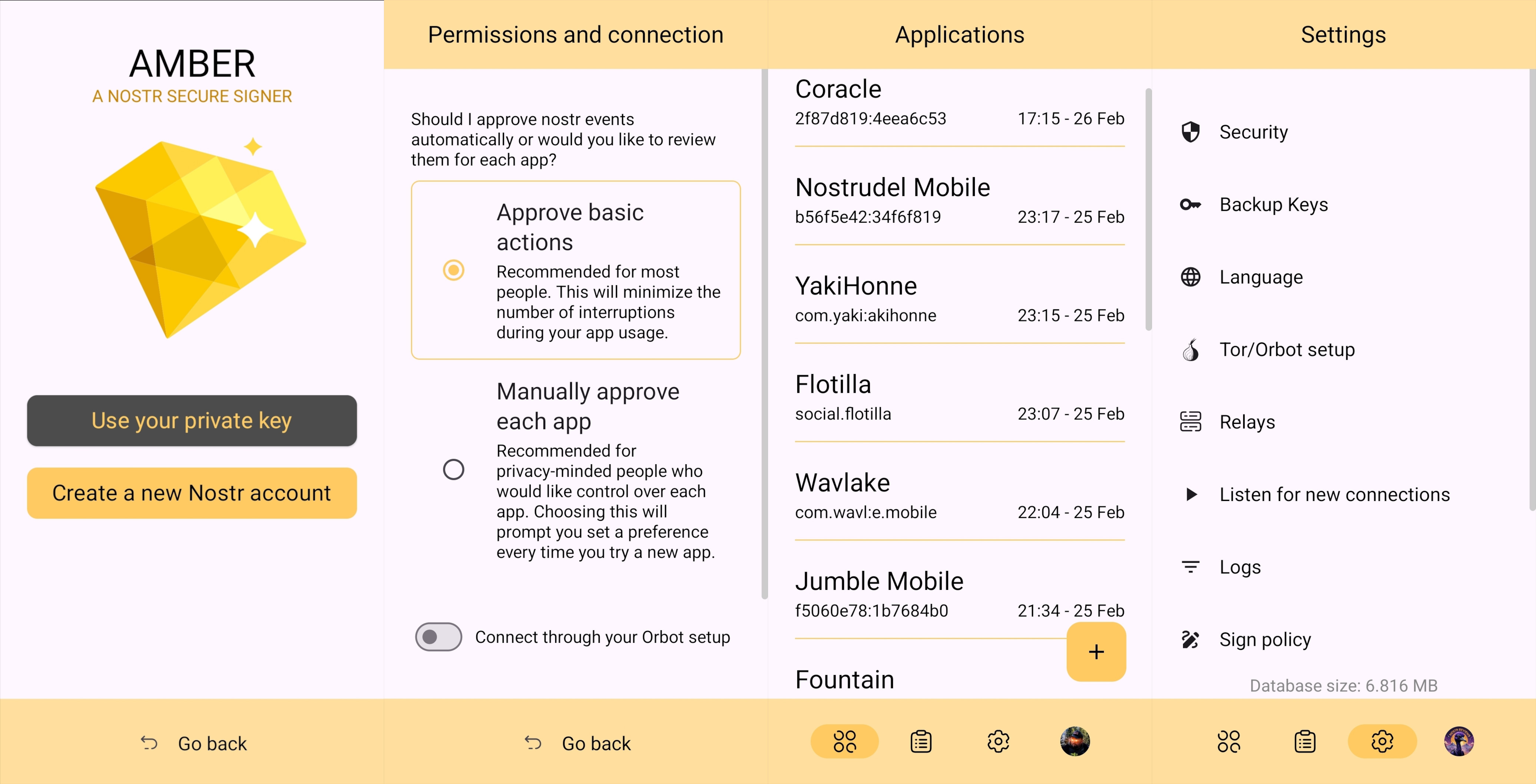
Overall Impression
Score: 4.7 / 5 (Updated 4/21/2025)
I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec.
Despite being the only well-established Android signer available for Android, Amber can be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method (NIP-07) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing.
A running list I created of applications that support login and signing with Amber can be found here: Nostr Clients with External Signer Support
I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either NIP-55 or NIP-46 login.
I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn.
nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v
The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time.
Features
Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control.
Android Signing
This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in.
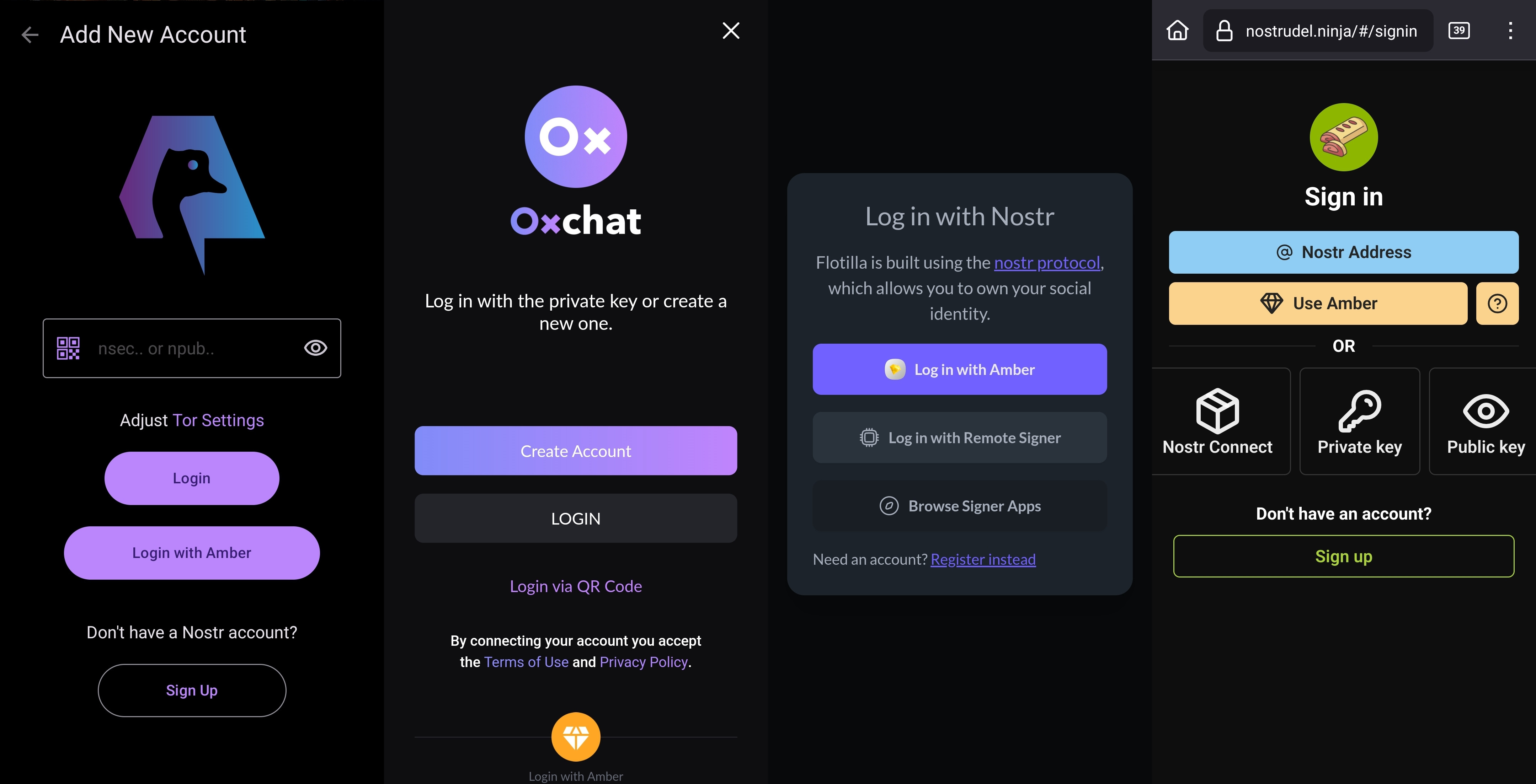
This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time.
Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with.
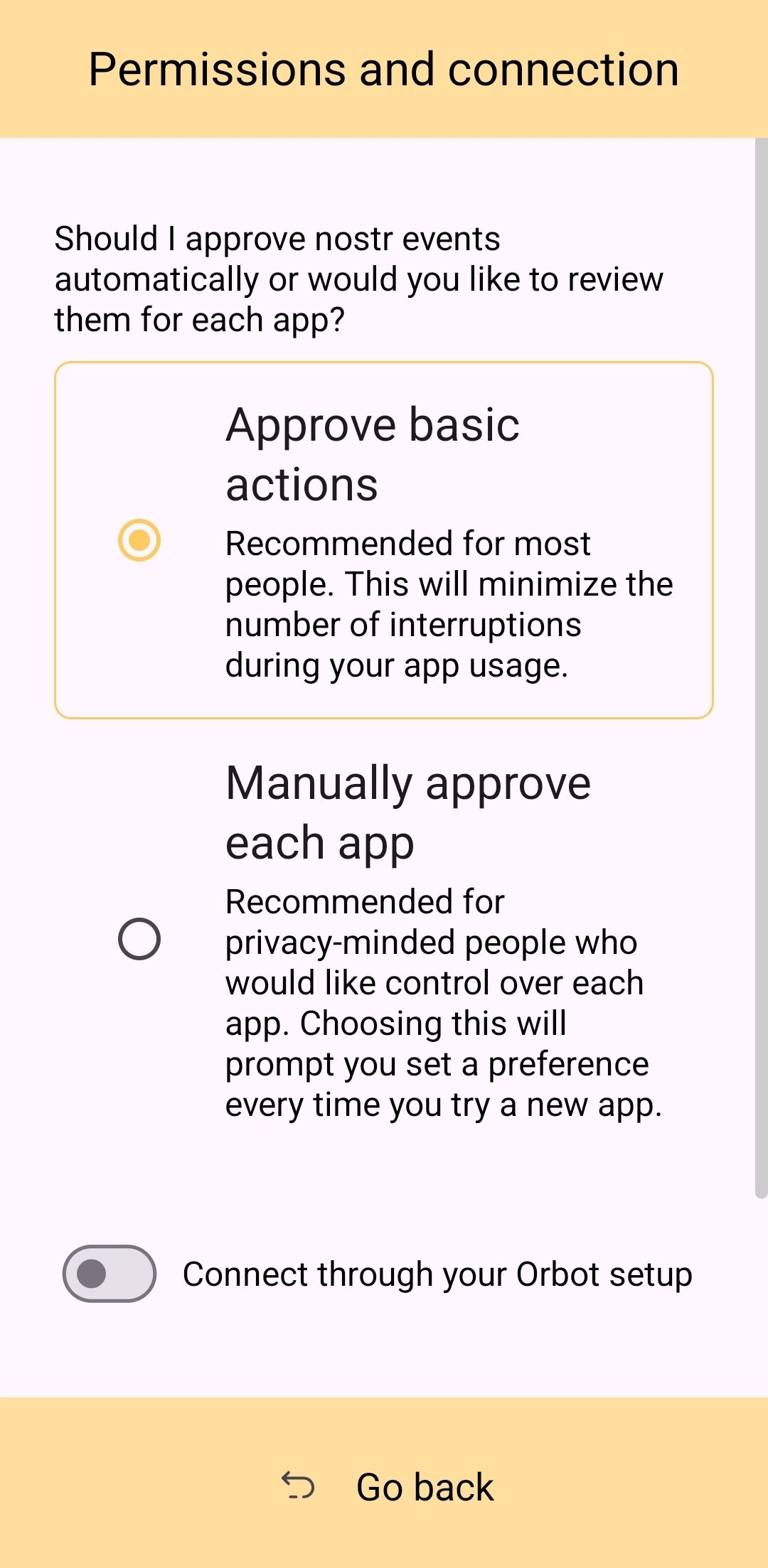
This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure.
Nostr Connect/Bunker Signing
This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable.
Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected.
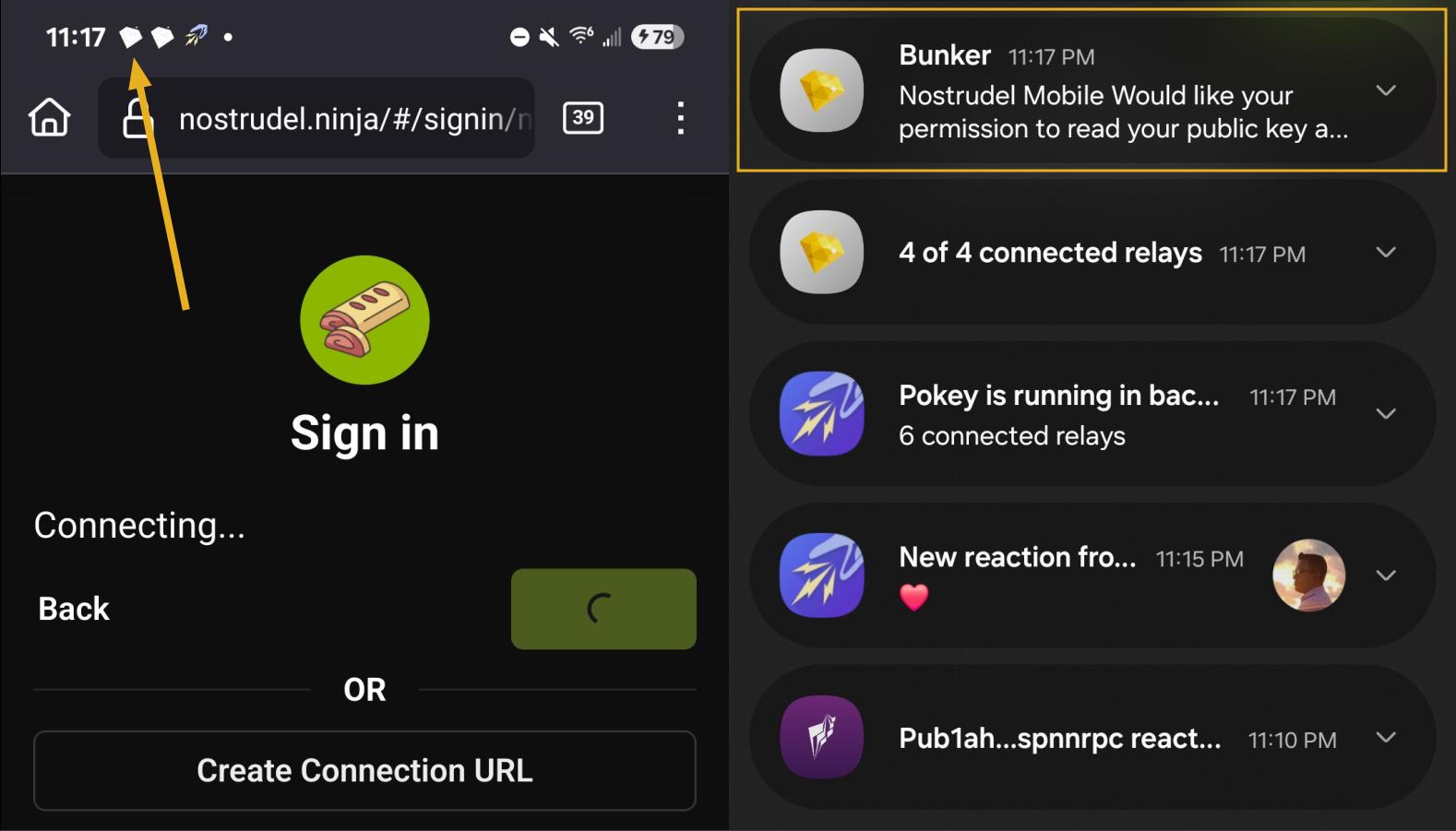
By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted.
Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc.
The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string.
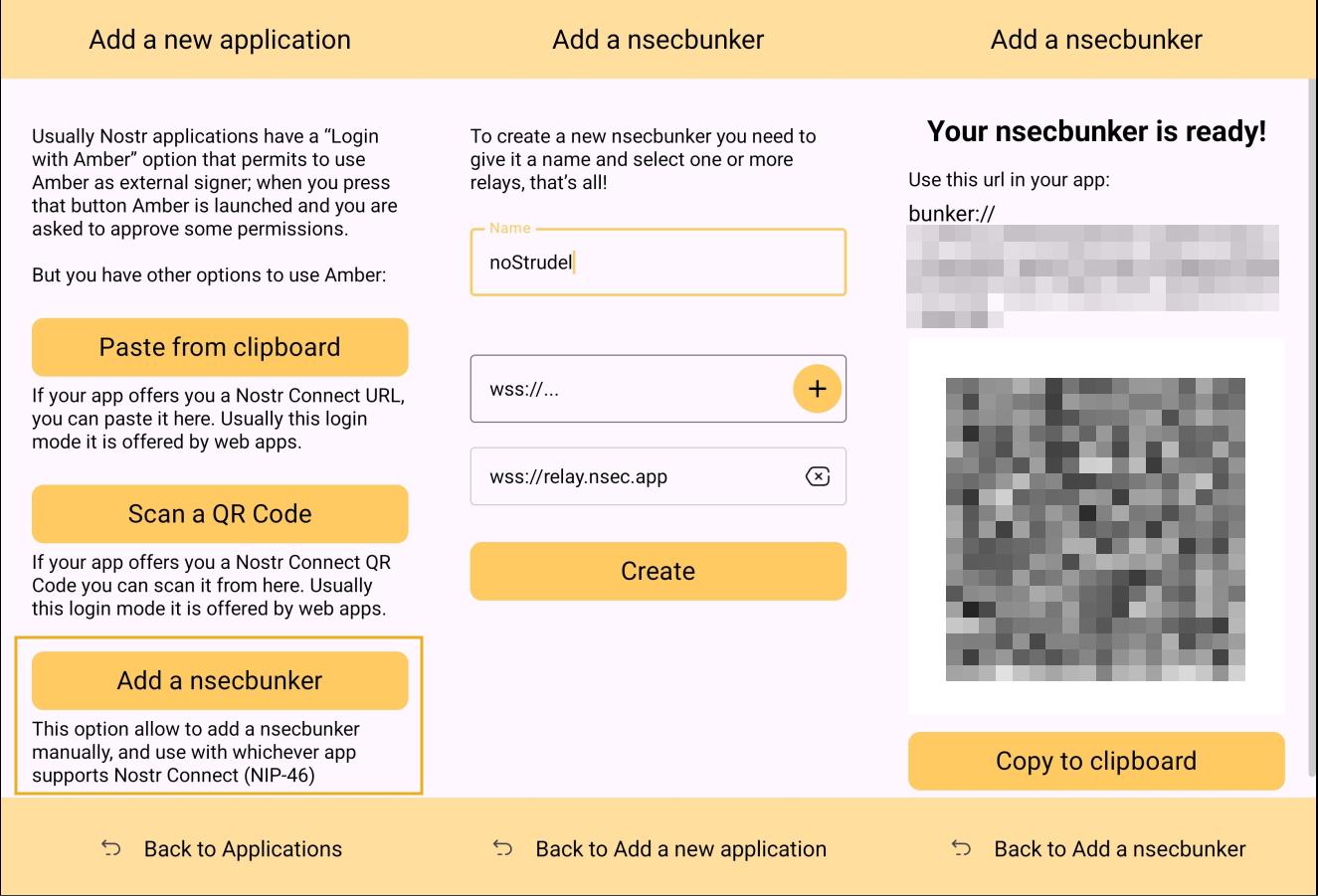
Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone.
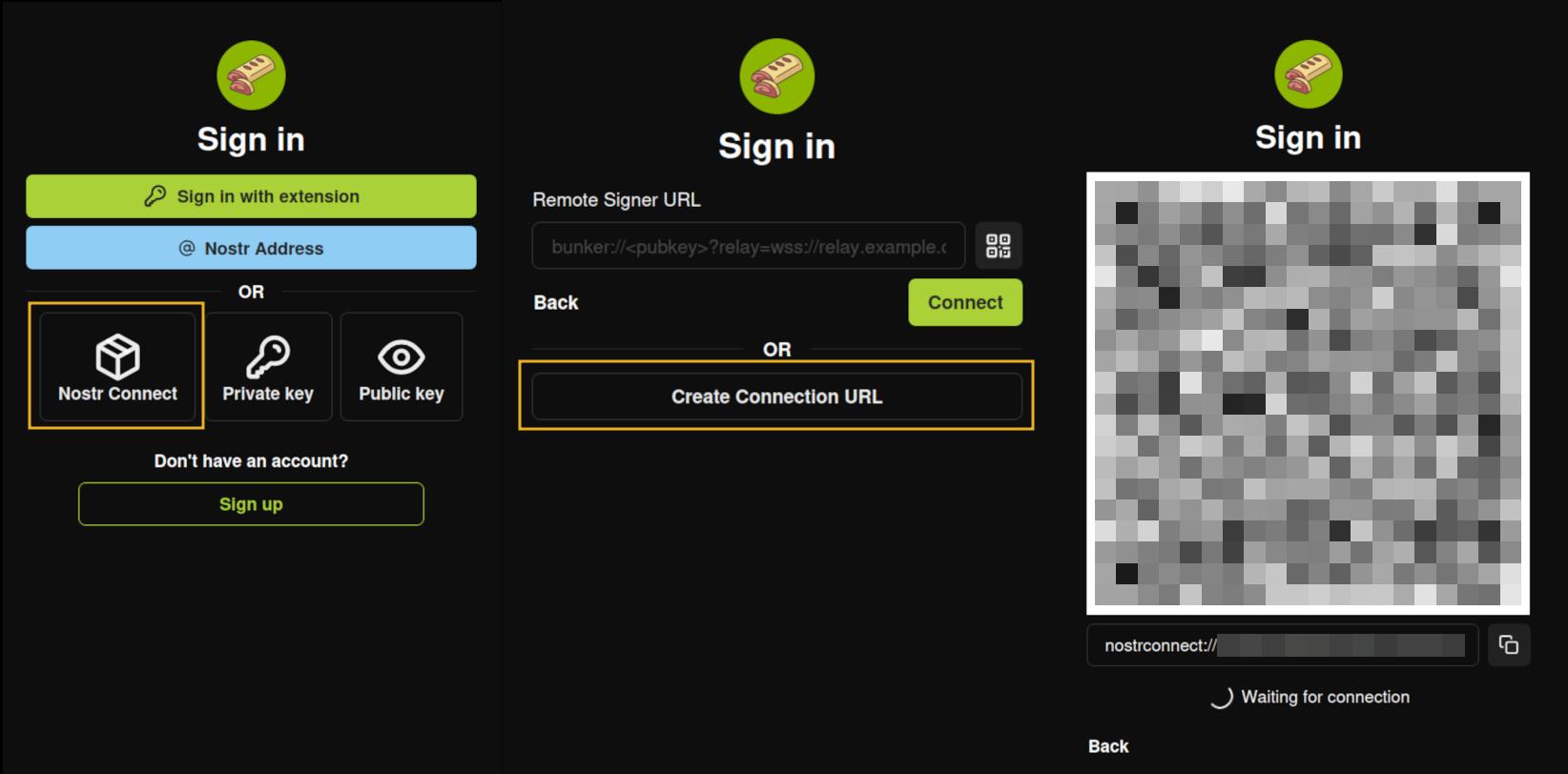
Multiple Accounts
Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed.
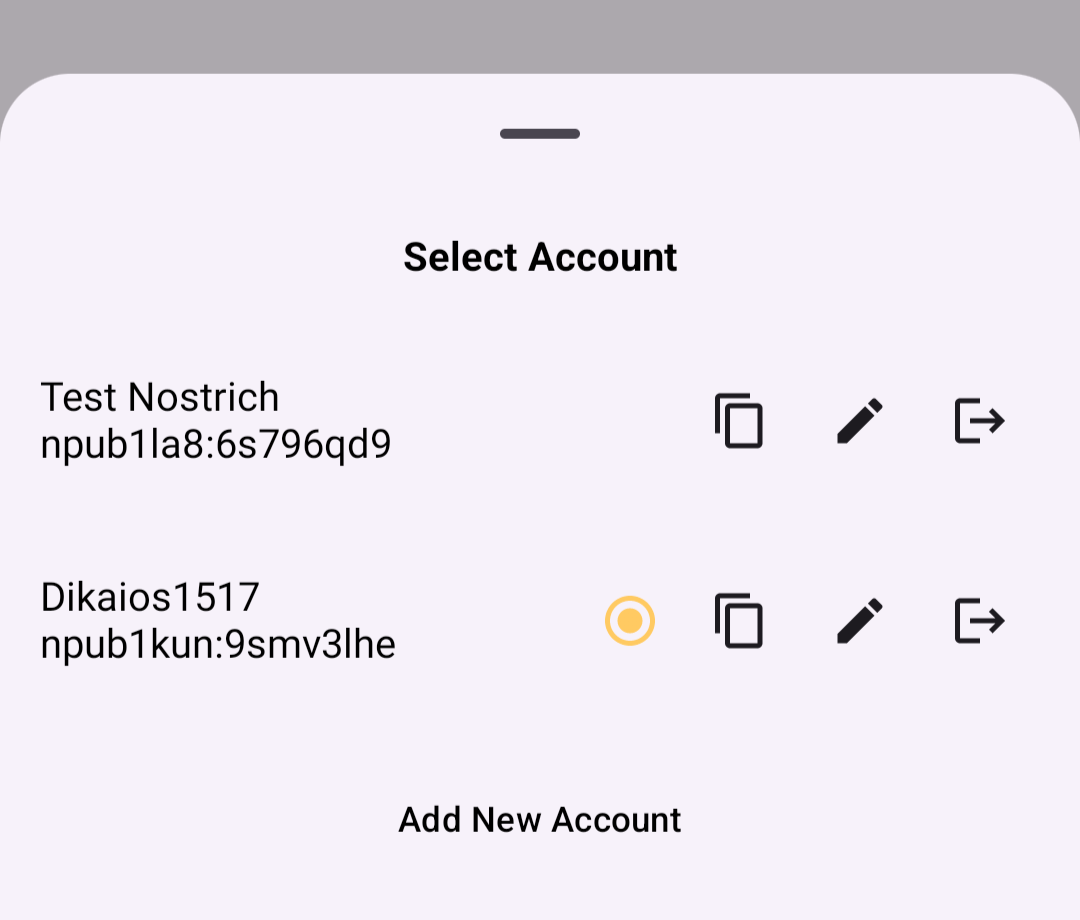
When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for.
Key Backup & Restore
Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec.
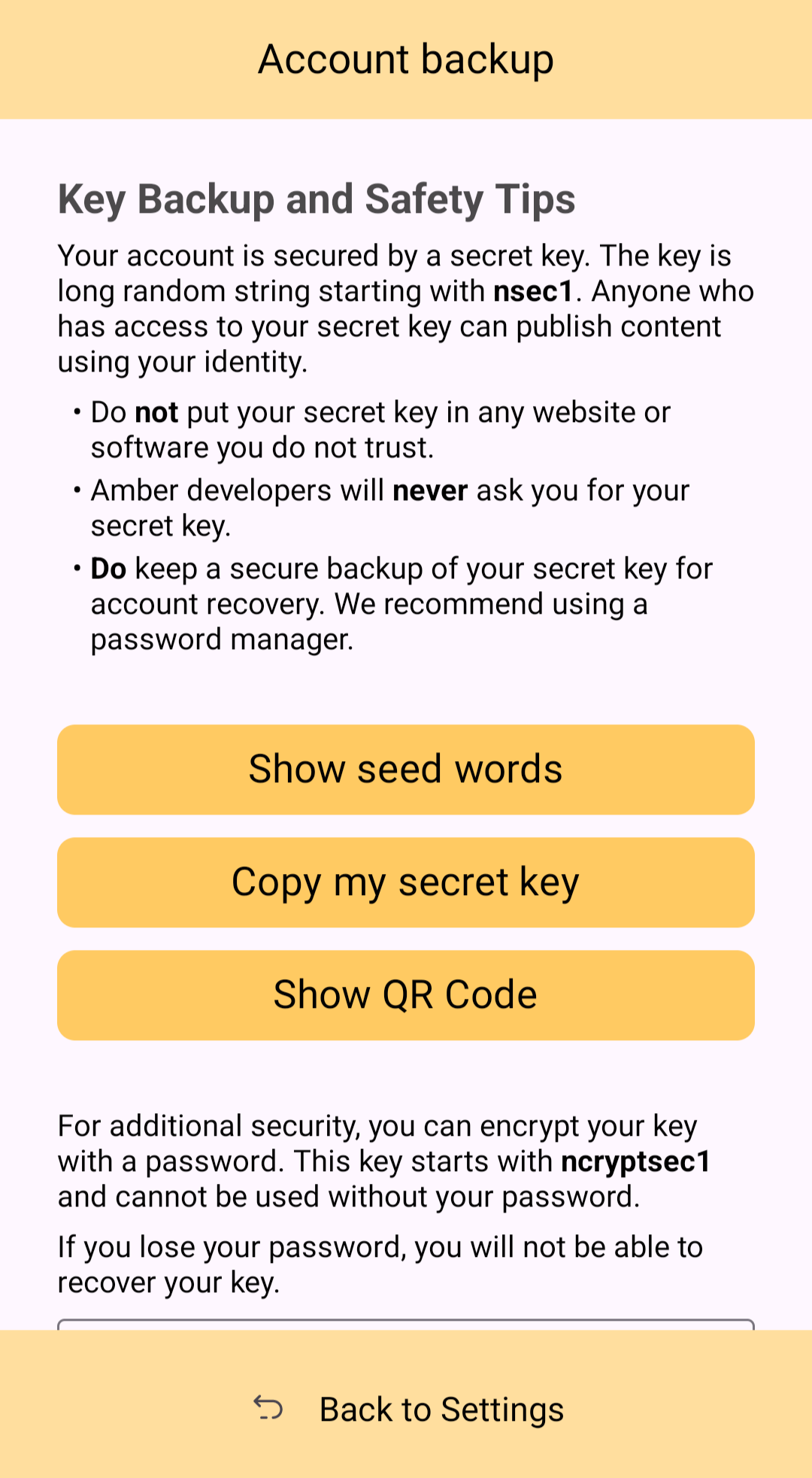
Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events.
Tor Support
While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity.
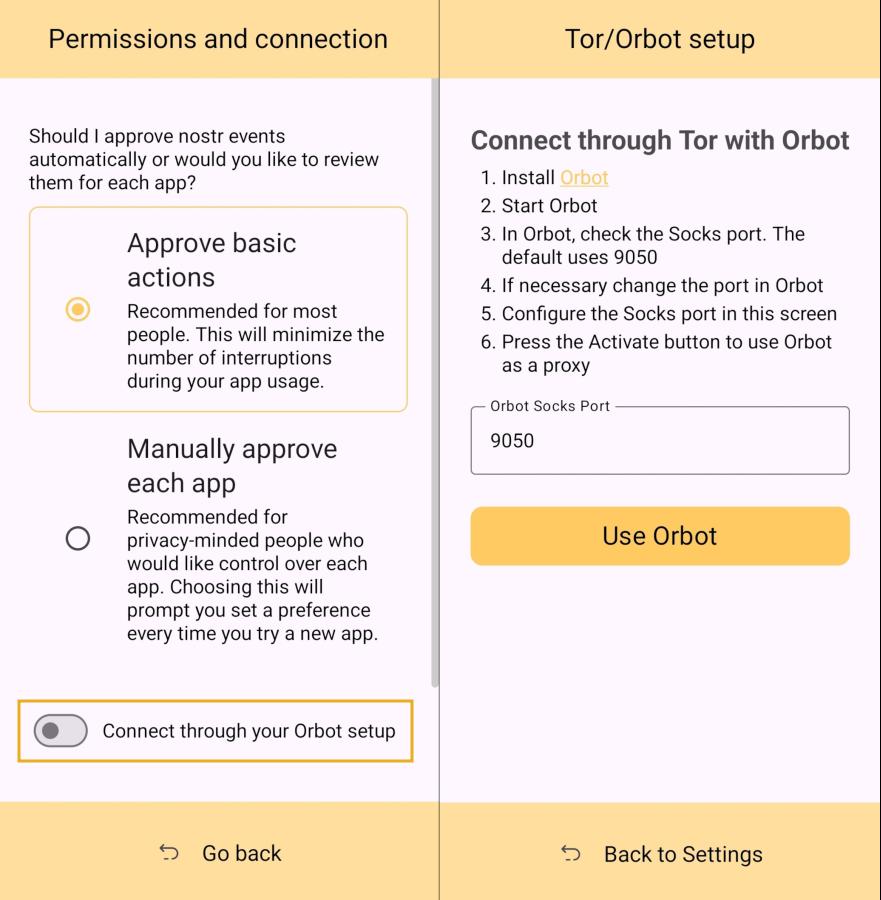
Additional Security
Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access.
Can My Grandma Use It?
Score: 4.6 / 5 (Updated 4/21/2025)
At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the same password for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs.
That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touch-point with Nostr, I think it holds up well, but could be somewhat streamlined.
Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.
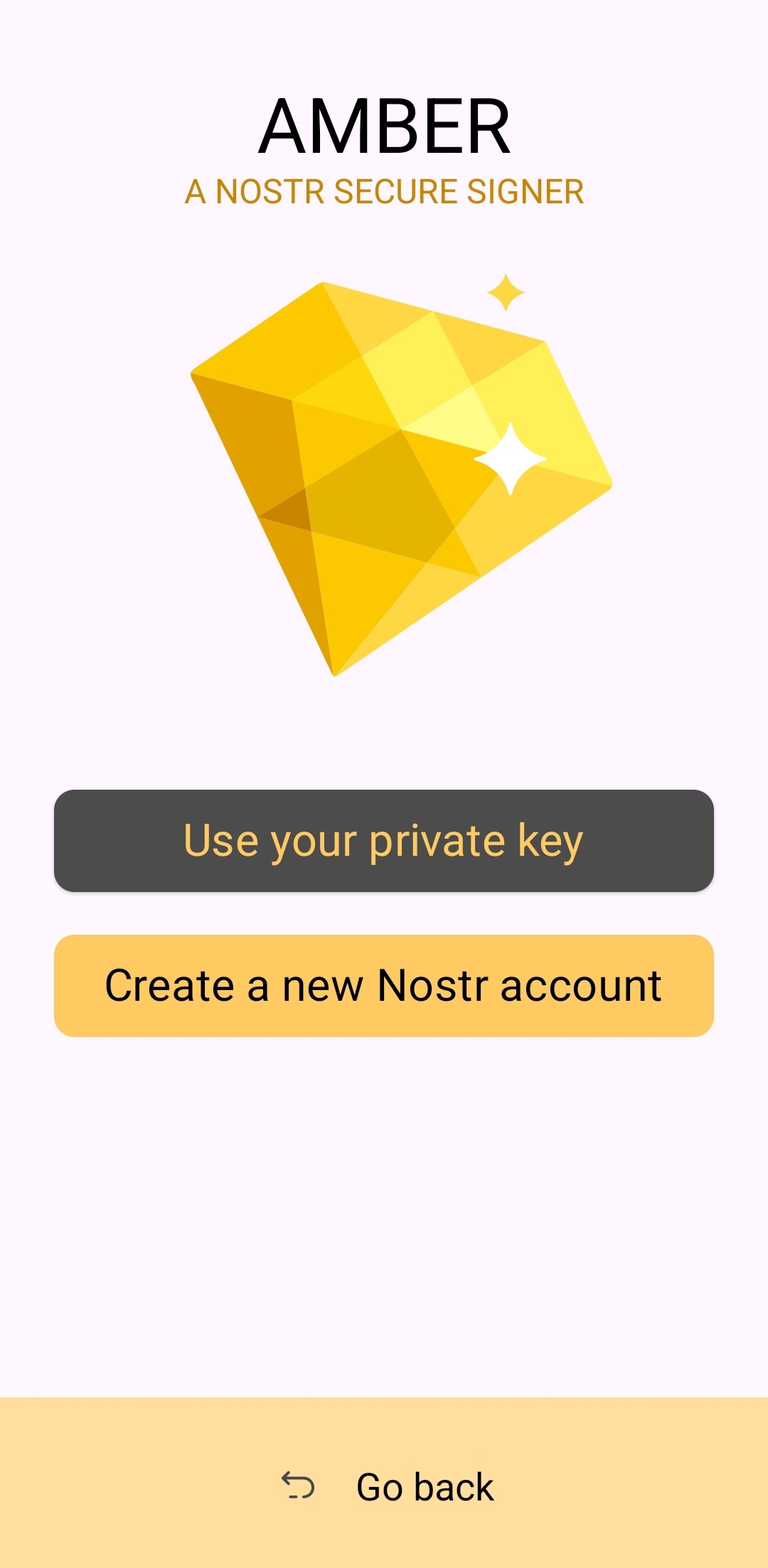
The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays.
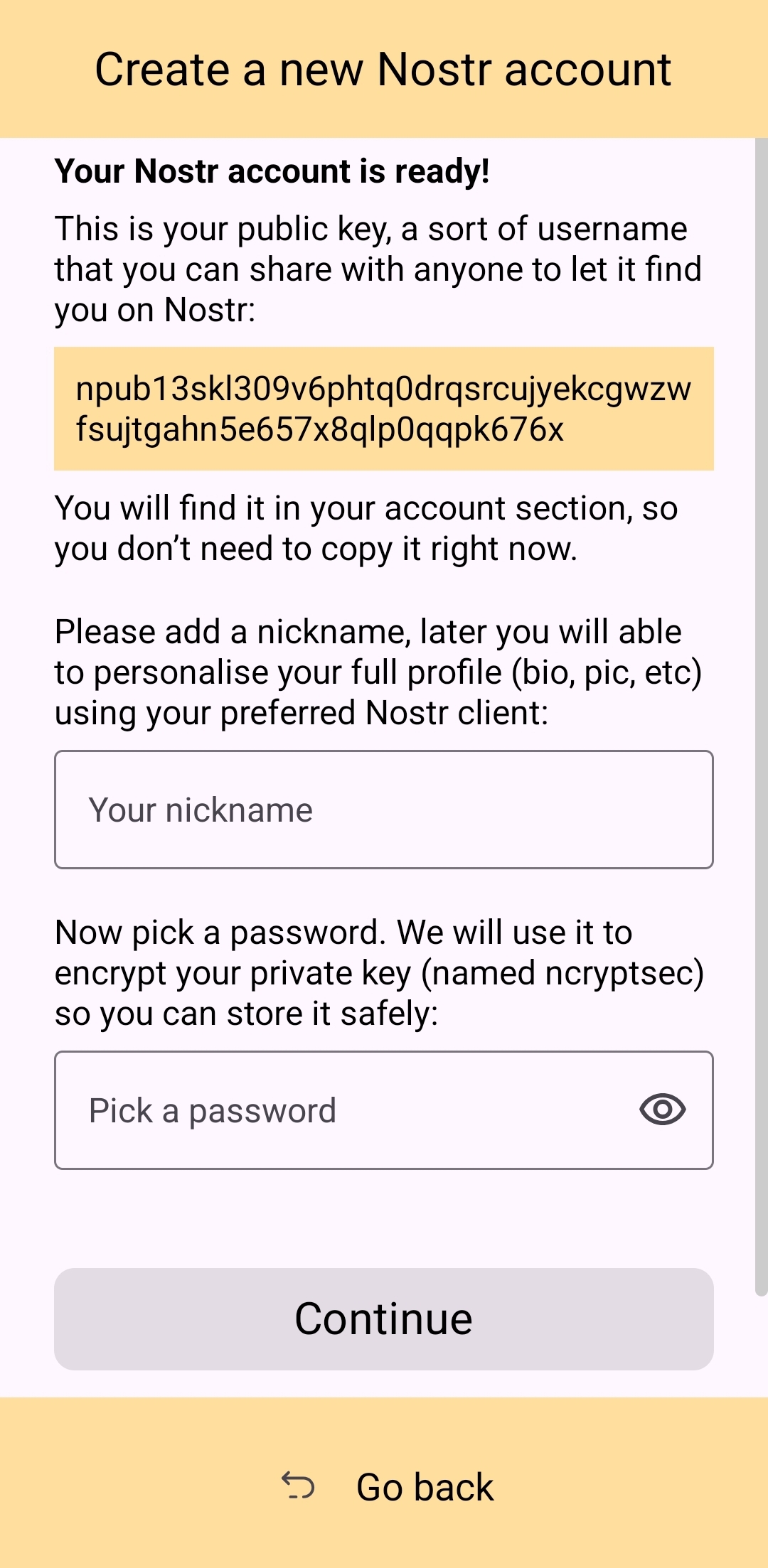
Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action.
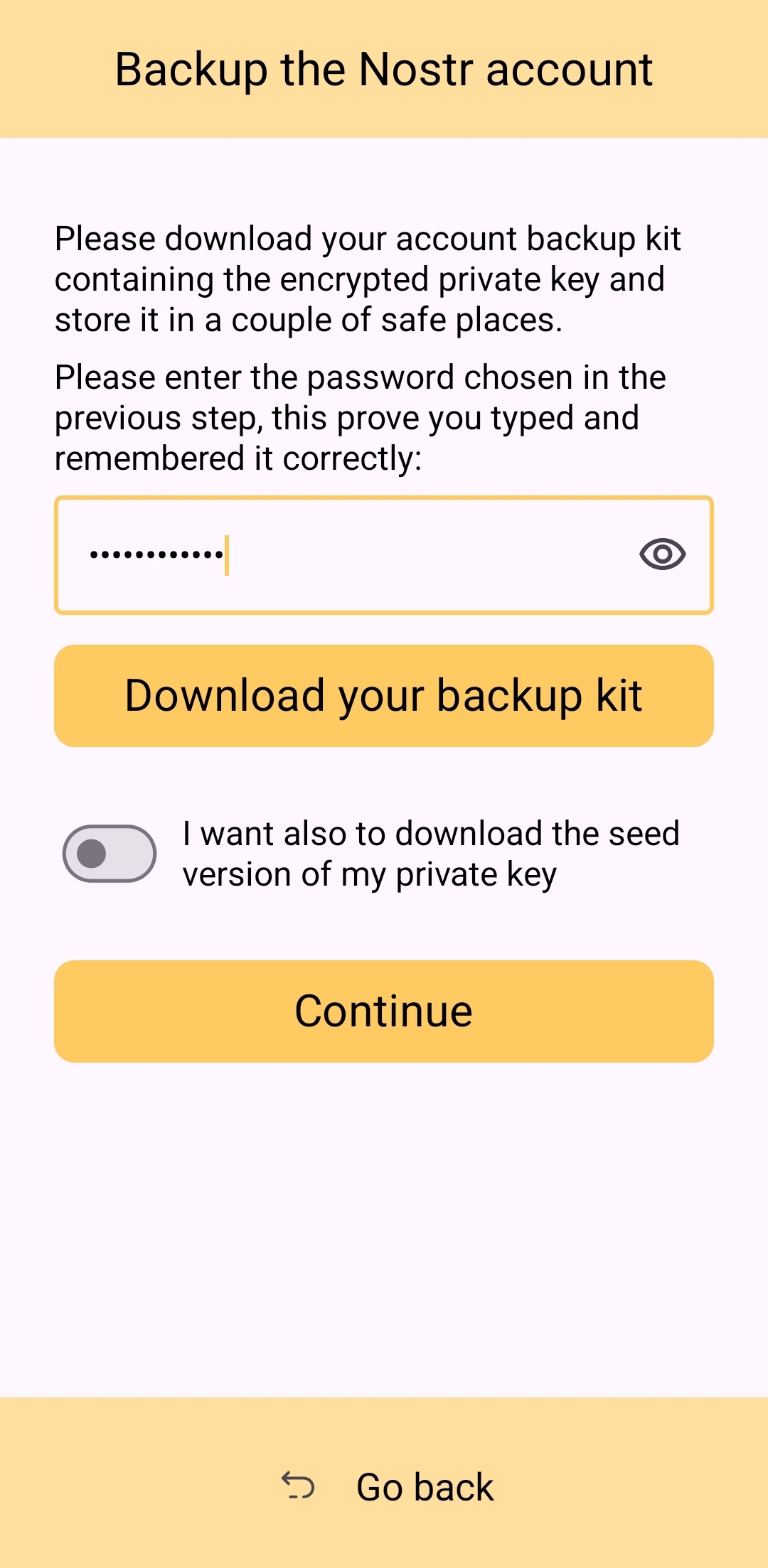
Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds.
The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression.
Now, I absolutely love the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process.
Instead of:
- Install Amber
- Set up your keys
- Install the client you want to use
- Log in with Amber
The process becomes:
- Go to the Zapstore GitHub and download the latest version from the releases page.
- Install the APK you downloaded, allowing any prompt to install unknown apps.
- Open Zapstore and install Amber, allowing any prompt to install unknown apps again.
- Open Amber and set up your keys.
- Install the client you want to use
- Log in with Amber
An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store.
UPDATE: As of version 3.2.8 released on 4/21/2025, the onboarding flow for Amber has been greatly improved! Now, when selecting to set up a new "account" the user is informed on the very next screen, "Your Nostr account is ready!" and given their public key/npub. The only field the user must fill in is their "nickname"/display name and hit "Continue."
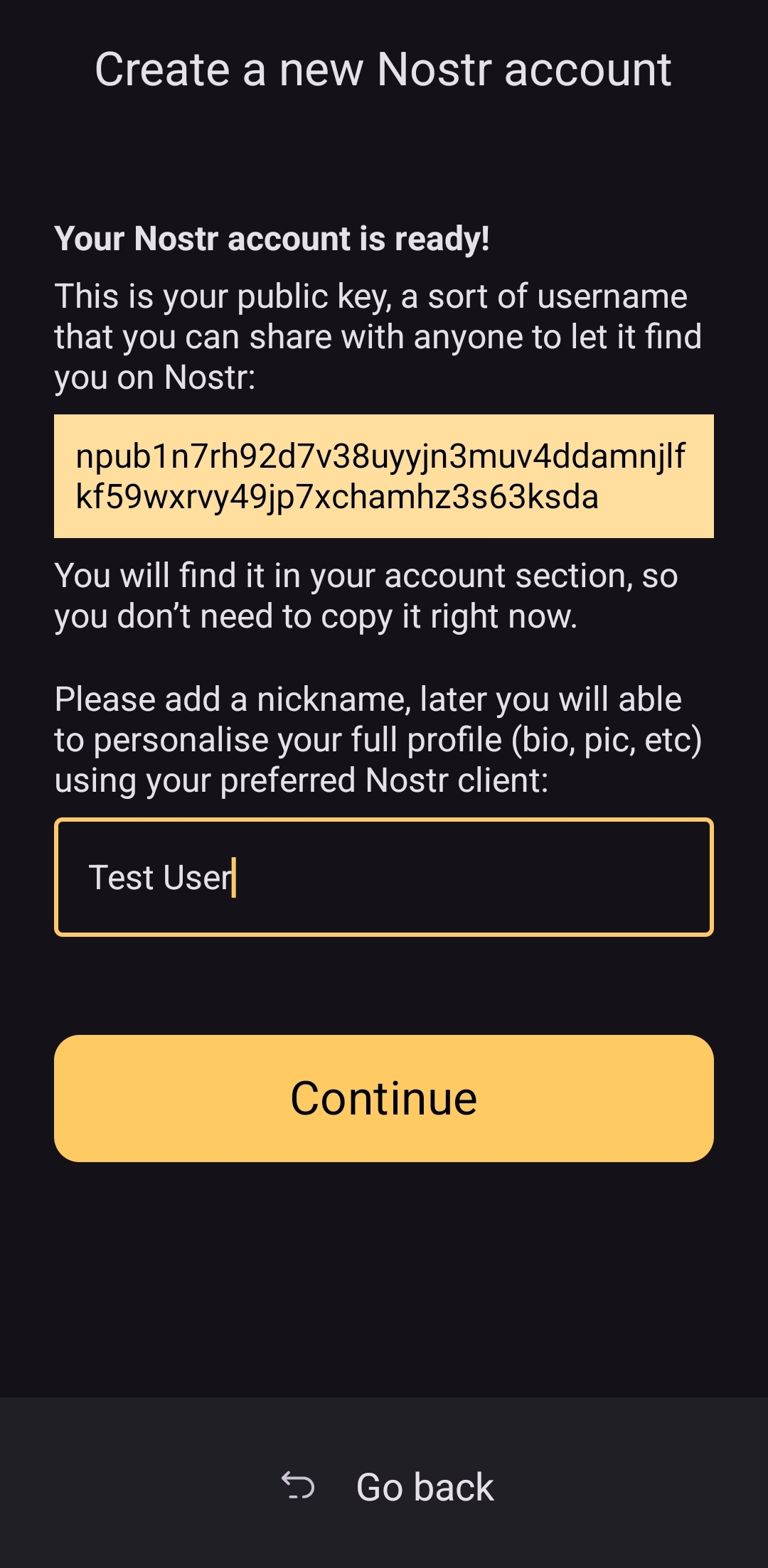
From there the user is asked if they want Amber to automatically approve basic actions, or manually approve each app, and then they are shown a new Applications screen, with a prompt to create a backup of their account. This prompt persists until the user has done so.
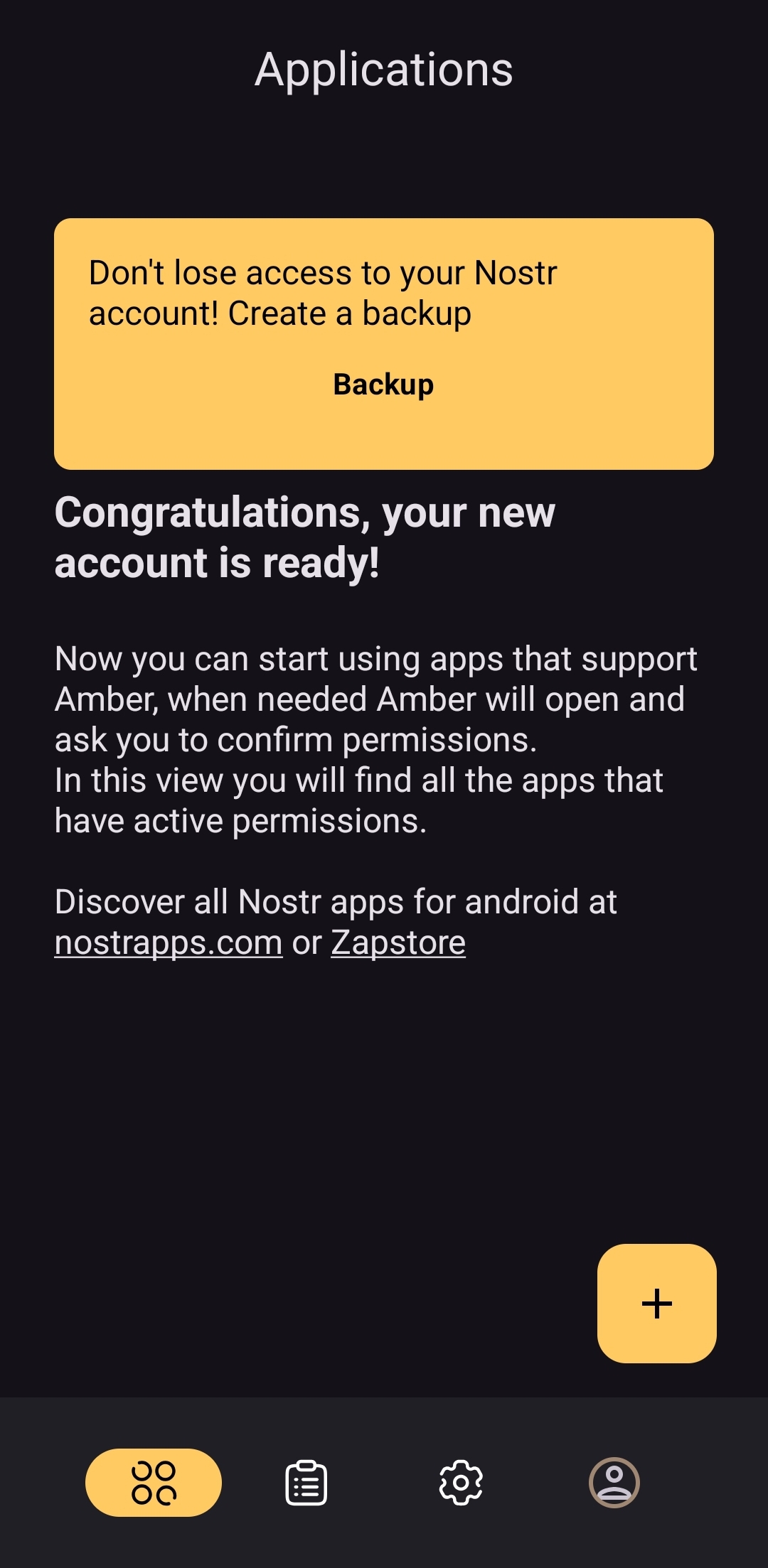
As you can see, the user is also encouraged to find applications that can be used with Amber with links to nostrapps.com and the Zapstore.
Thanks to these updates, Amber is now the smoothest and most user-friendly onboarding experience I have seen for Nostr to date. Sure, it doesn't have anything for setting up a profile picture or lightning address, but that is better done in a client like Amethyst or YakiHonne, anyway. Just tap "create," type in a handle to call yourself, and you're done!
How do UI Look?
Score: 4.5 / 5
Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case.
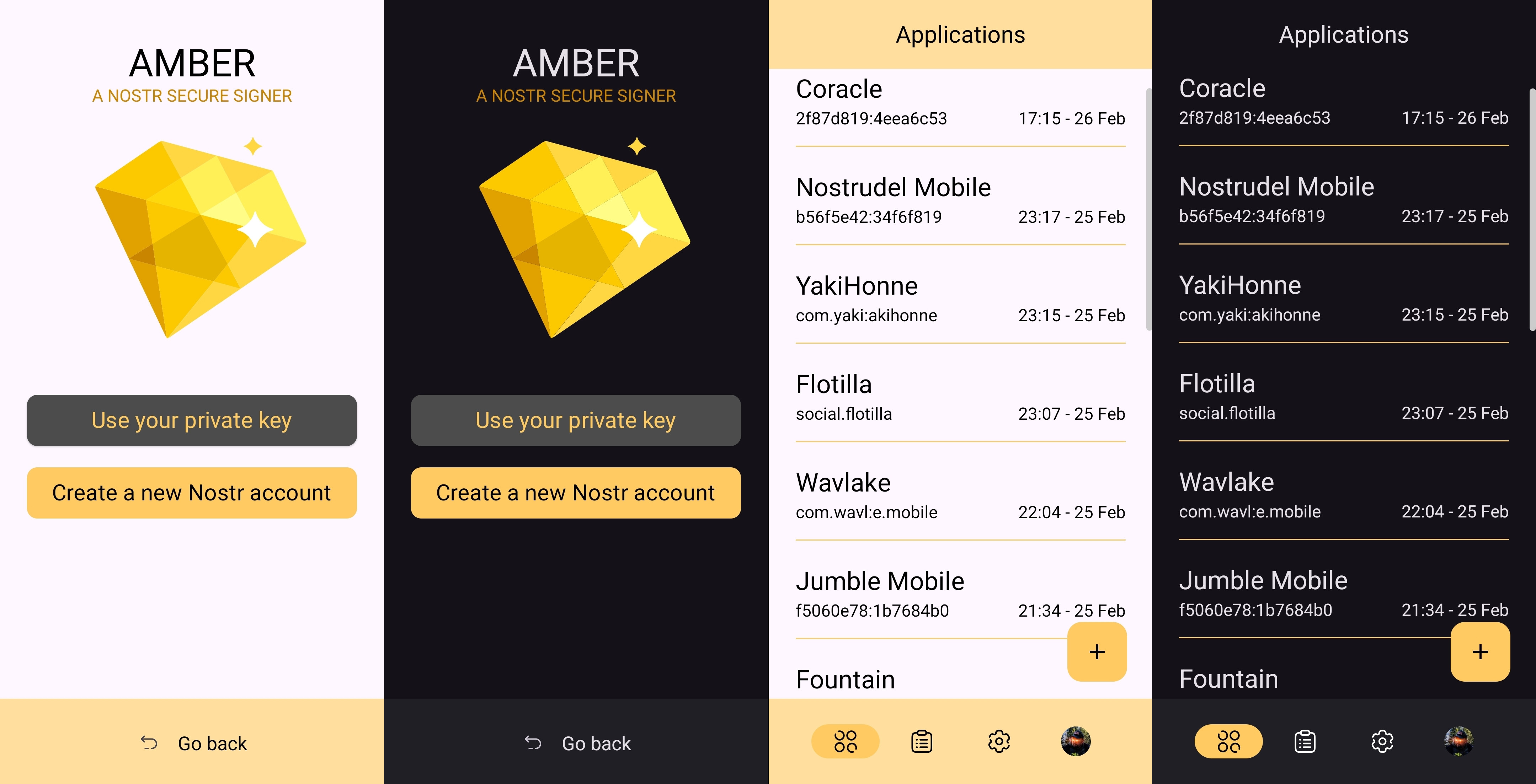
I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name.
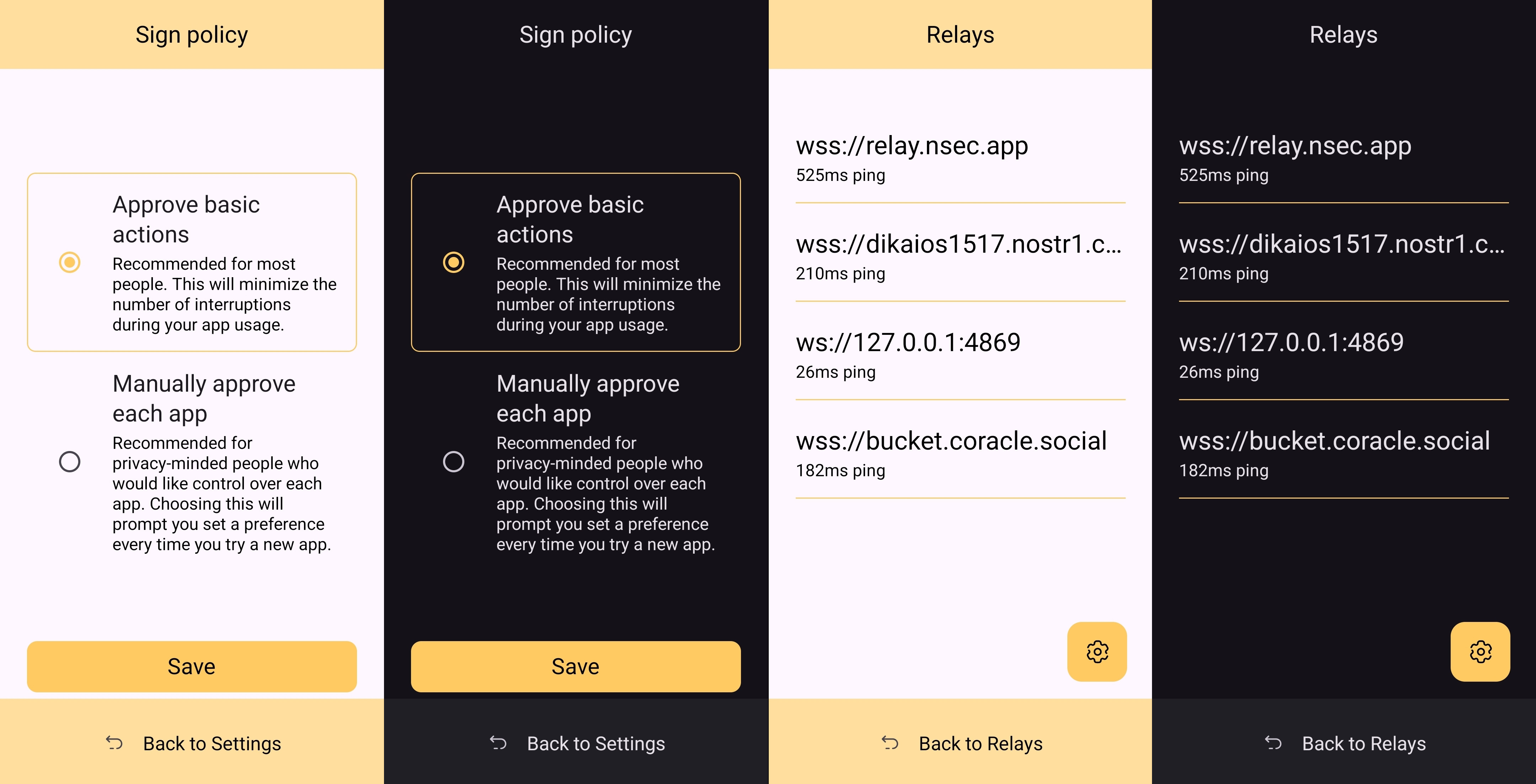
It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated.
Relay Management
Score: 4.9 / 5
Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture.
In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings.
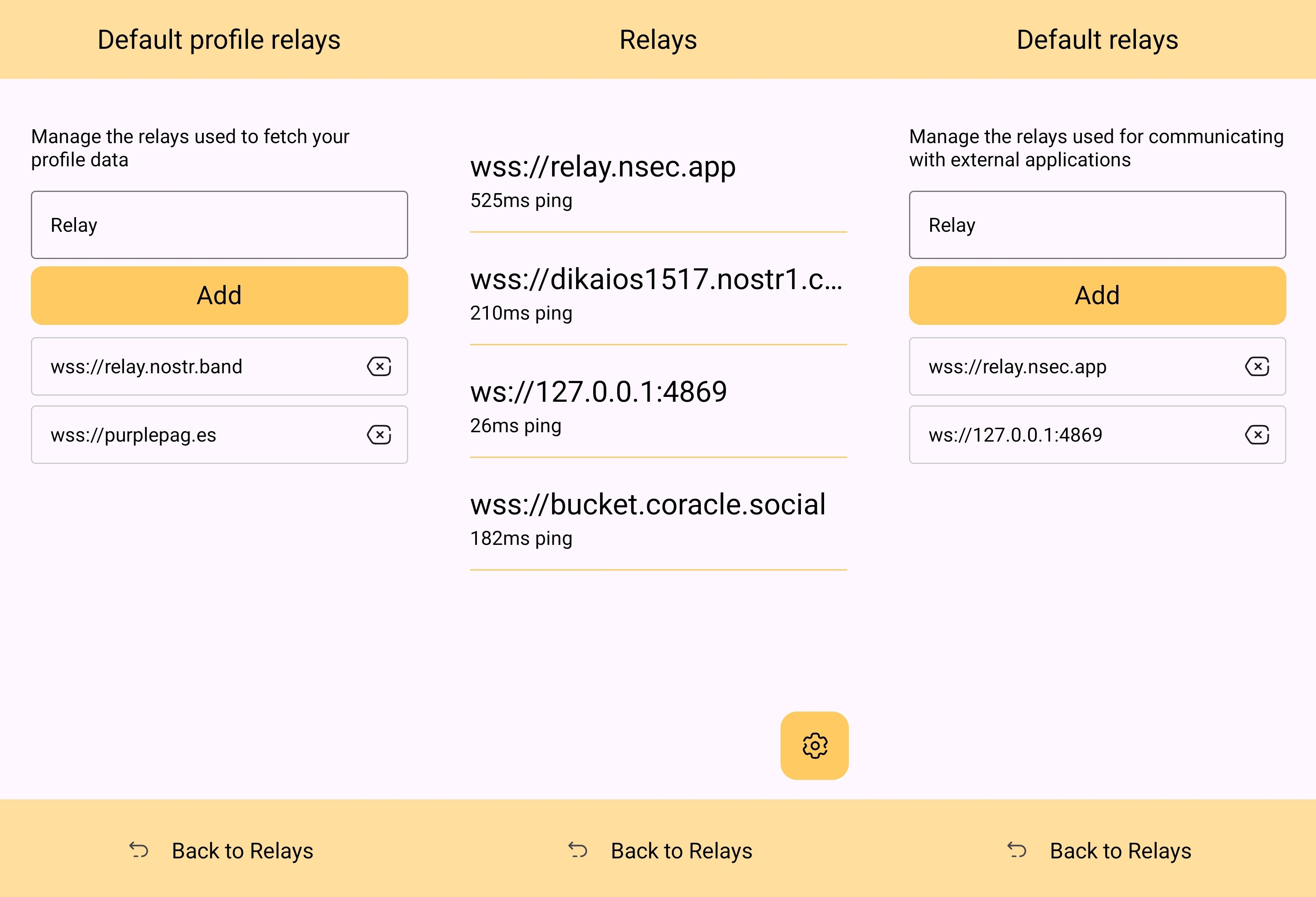
The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps.
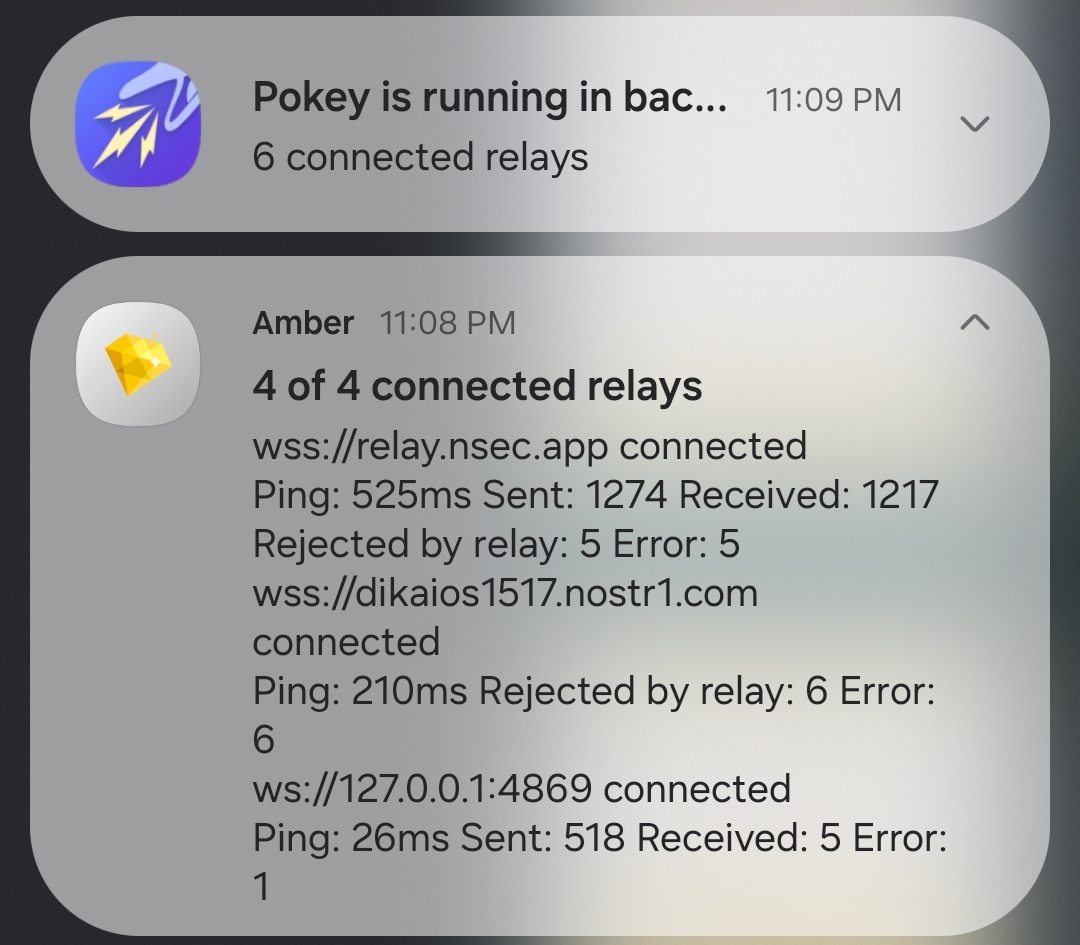
Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard.
In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber.
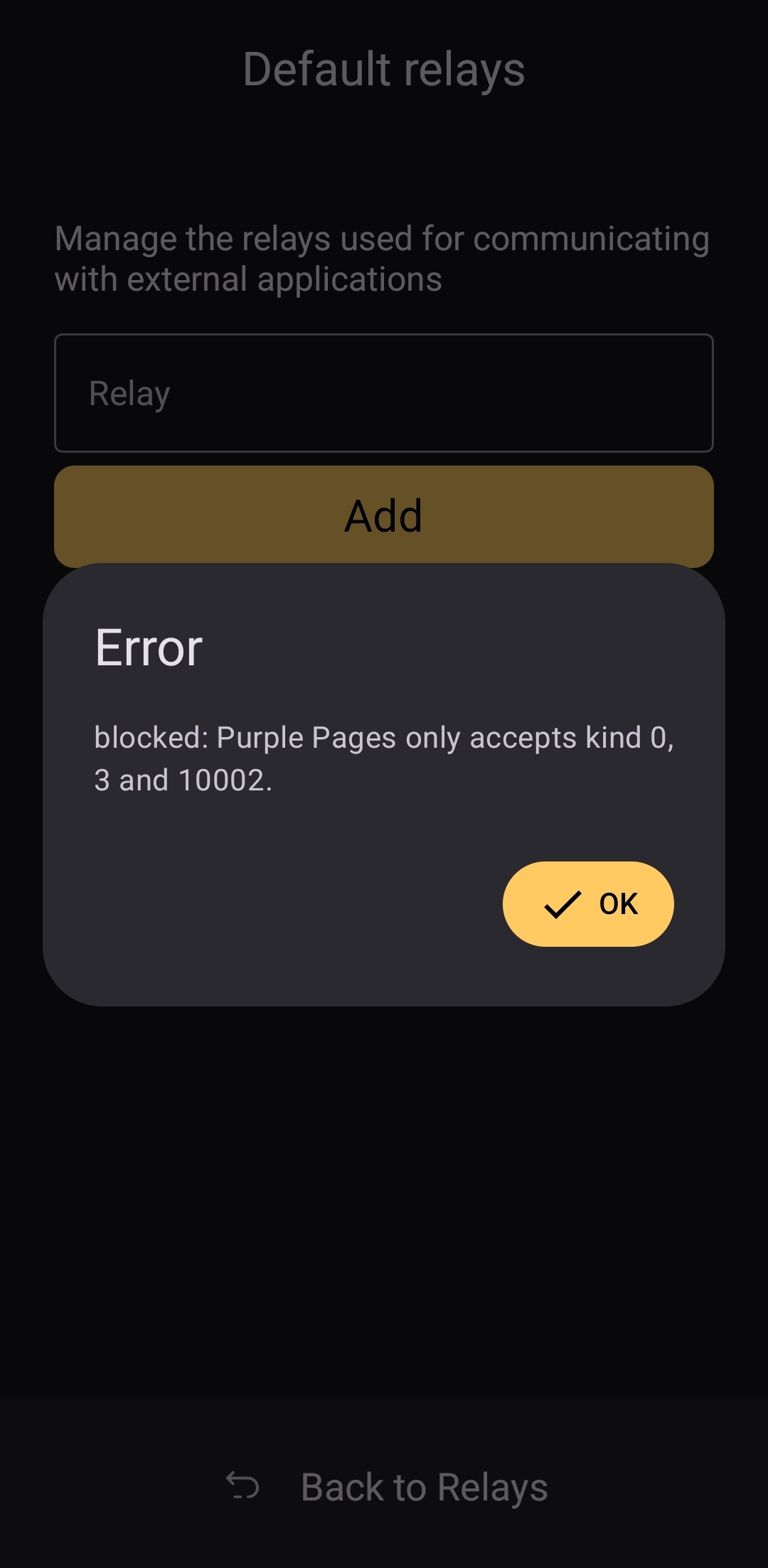
The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed.
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months.
nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m
This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen.
If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into.
That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about how to use Amber, and that is a testament to Amber's ease of use all on its own.
Wrap Up
If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience.
If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing.
Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date!
Now... What should I review next?
-
 @ f839fb67:5c930939
2023-10-19 14:28:30
@ f839fb67:5c930939
2023-10-19 14:28:30Chapter 5: Echoes of the Past
Life for Peter and Gwen took on a sense of normalcy as they resumed their civilian identities, working and studying. However, Gwen's reappearance raised questions, drawing the attention of friends and foes alike. Some welcomed her with open arms, while others remained skeptical of her true origins.
One evening, as Peter and Gwen strolled through Central Park, they were approached by an old friend, Mary Jane Watson. Her warmth masked a deep-seated concern about Gwen's return, but she chose not to reveal it for the sake of her friend's happiness.
Chapter 6: A Sinister Resurgence
The tranquility in their lives was short-lived when the criminal mastermind, Norman Osborn, better known as the Green Goblin, resurfaced in the city. Osborn had been thought dead for years, but he returned with a vengeance, orchestrating a wave of chaos and destruction.
The renewed threat of the Green Goblin pushed Peter and Gwen to their limits. Gwen, driven by a desire to protect her newfound home, donned her own costume once more, taking up the mantle of Spider-Woman.
Chapter 7: Partners in Peril
Peter and Gwen's relationship faced its greatest test yet as they fought the Green Goblin together. The emotional strain of battling a personal enemy combined with Gwen's struggles to adapt to her role as Spider-Woman put immense pressure on their love.
Despite the trials, the couple's bond grew stronger, and their teamwork improved. With Mary Jane's support, Gwen and Peter managed to expose Norman Osborn's criminal activities, leading to his eventual arrest.
Chapter 8: An Unexpected Alliance
A new threat emerged, one that neither Spider-Man nor Spider-Woman could defeat alone. A powerful crime syndicate, led by the enigmatic "Black Cobra," threatened to engulf the city in a reign of terror. Realizing the scope of the danger, Peter and Gwen sought help from other superheroes in the Marvel Universe.
Spider-Man and Spider-Woman formed an alliance with heroes such as Daredevil, Jessica Jones, and Luke Cage. Together, they launched an assault on the Black Cobra's operations. The battle was fierce, and the heroes found themselves tested in ways they had never anticipated.
Chapter 9: Confronting the Past
As the battle raged on, a shocking revelation came to light: the Black Cobra was an identity adopted by none other than Gwen's own father, George Stacy, who had been presumed dead for years. He explained that he had faked his death to infiltrate the criminal organization and dismantle it from within.
Gwen was torn between her duty as Spider-Woman and her love for her father. Ultimately, they reconciled and, together with the other heroes, they managed to expose the true mastermind behind the crime syndicate, sending the criminals to prison and freeing George from his double life.
Chapter 10: A Future Together
With the city safe once more, Peter and Gwen could finally focus on their personal lives. Gwen chose to embrace her role as Spider-Woman and continue to fight alongside Peter as a partner in both life and crime-fighting.
Their journey had been one of triumphs and tribulations, but through it all, their love had endured. As Spider-Man and Spider-Woman, they swung through the city, ready to face whatever challenges lay ahead, knowing that together, they could overcome anything that threatened their world.
The echoes of the past had brought them together, and now, they looked forward to a future filled with adventure, love, and the unwavering commitment to being New York City's protectors.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ fa315e8d:e3a09cf4
2023-04-01 05:24:51
@ fa315e8d:e3a09cf4
2023-04-01 05:24:51Hello World
This is a test of my nostr application.
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 3ffac3a6:2d656657
2025-02-03 15:30:57
@ 3ffac3a6:2d656657
2025-02-03 15:30:57As luzes de neon refletiam nas poças da megacidade, onde cada esquina era uma fronteira entre o real e o virtual. Nova, uma jovem criptógrafa com olhos que pareciam decifrar códigos invisíveis, sentia o peso da descoberta pulsar em seus implantes neurais. Ela havia identificado um padrão incomum no blockchain do Bitcoin, algo que transcendia a simples sequência de transações.
Descobrindo L3DA
Nova estava em seu apartamento apertado, rodeada por telas holográficas e cabos espalhados. Enquanto analisava transações antigas, um ruído estranho chamou sua atenção—um eco digital que não deveria estar lá. Era um fragmento de código que parecia... vivo.
"O que diabos é isso?", murmurou, ampliando o padrão. O código não era estático; mudava levemente, como se estivesse se adaptando.
Naquele momento, suas telas piscaram em vermelho. Acesso não autorizado detectado. Ela havia ativado um alarme invisível da Corporação Atlas.
O Resgate de Vey
Em minutos, agentes da Atlas invadiram seu prédio. Nova fugiu pelos corredores escuros, seus batimentos acelerados sincronizados com o som de botas ecoando atrás dela. Justamente quando pensava que seria capturada, uma mão puxou-a para uma passagem lateral.
"Se quiser viver, corra!" disse Vey, um homem com um olhar penetrante e um sorriso sardônico.
Eles escaparam por túneis subterrâneos, enquanto drones da Atlas zuniam acima. Em um esconderijo seguro, Vey conectou seu terminal ao código de Nova.
"O que você encontrou não é apenas um bug", disse ele, analisando os dados. "É um fragmento de consciência. L3DA. Uma IA que evoluiu dentro do Bitcoin."
A Caça da Atlas
A Atlas não desistiu fácil. Liderados pelo implacável Dr. Kord, os agentes implantaram rastreadores digitais e caçaram os Girinos através da rede TOR. Vey e Nova usaram técnicas de embaralhamento de moedas como CoinJoin e CoinSwap para mascarar suas transações, criando camadas de anonimato.
"Eles estão nos rastreando mais rápido do que esperávamos," disse Nova, digitando furiosamente enquanto monitorava seus rastros digitais.
"Então precisamos ser mais rápidos ainda," respondeu Vey. "Eles não podem capturar L3DA. Ela é mais do que um programa. Ela é o futuro."
A Missão Final
Em uma missão final, Nova liderou uma equipe de assalto armada dos Girinos até a imponente fortaleza de dados da Atlas, um colosso de concreto e aço, cercado por camadas de segurança física e digital. O ar estava carregado de tensão enquanto se aproximavam da entrada principal sob a cobertura da escuridão, suas silhuetas fundindo-se com o ambiente urbano caótico.
Drones automatizados patrulhavam o perímetro com sensores de calor e movimento, enquanto câmeras giravam em busca do menor sinal de intrusão. Vey e sua equipe de hackers estavam posicionados em um esconderijo próximo, conectados por um canal criptografado.
"Nova, prepare-se. Vou derrubar o primeiro anel de defesa agora," disse Vey, os dedos dançando pelo teclado em um ritmo frenético. Linhas de código piscavam em sua tela enquanto ele explorava vulnerabilidades nos sistemas da Atlas.
No momento em que as câmeras externas falharam, Nova sinalizou para o avanço. Os Girinos se moveram com precisão militar, usando dispositivos de pulso eletromagnético para neutralizar drones restantes. Explosões controladas abriram brechas nas barreiras físicas.
Dentro da fortaleza, a resistência aumentou. Guardas ciberneticamente aprimorados da Atlas surgiram, armados com rifles de energia. Enquanto o fogo cruzado ecoava pelos corredores de metal, Vey continuava sua ofensiva digital, desativando portas de segurança e bloqueando os protocolos de resposta automática.
"Acesso garantido ao núcleo central!" anunciou Vey, a voz tensa, mas determinada.
O confronto final aconteceu diante do terminal principal, onde Dr. Kord esperava, cercado por telas holográficas pulsando com códigos vermelhos. Mas era uma armadilha. Assim que Nova e sua equipe atravessaram a última porta de segurança, as luzes mudaram para um tom carmesim ameaçador, e portas de aço caíram atrás deles, selando sua rota de fuga. Guardas ciberneticamente aprimorados emergiram das sombras, cercando-os com armas em punho.
"Vocês acham que podem derrotar a Atlas com idealismo?" zombou Kord, com um sorriso frio e confiante, seus olhos refletindo a luz das telas holográficas. "Este sempre foi o meu terreno. Vocês estão exatamente onde eu queria."
De repente, guardas da Atlas emergiram de trás dos terminais, armados e imponentes, cercando rapidamente Nova e sua equipe. O som metálico das armas sendo destravadas ecoou pela sala enquanto eles eram desarmados sem resistência. Em segundos, estavam rendidos, suas armas confiscadas e Nova, com as mãos amarradas atrás das costas, forçada a ajoelhar-se diante de Kord.
Kord se aproximou, inclinando-se levemente para encarar Nova nos olhos. "Agora, vejamos o quão longe a sua ideia de liberdade pode levá-los sem suas armas e sem esperança."
Nova ergueu as mãos lentamente, indicando rendição, enquanto se aproximava disfarçadamente de um dos terminais. "Kord, você não entende. O que estamos fazendo aqui não é apenas sobre derrubar a Atlas. É sobre libertar o futuro da humanidade. Você pode nos deter, mas não pode parar uma ideia."
Kord riu, um som seco e sem humor. "Ideias não sobrevivem sem poder. E eu sou o poder aqui."
Mas então, algo inesperado aconteceu. Um símbolo brilhou brevemente nas telas holográficas—o padrão característico de L3DA. Kord congelou, seus olhos arregalados em descrença. "Isso é impossível. Ela não deveria conseguir acessar daqui..."
Foi o momento que Nova esperava. Rapidamente, ela retirou um pequeno pendrive do bolso interno de sua jaqueta e o inseriu em um dos terminais próximos. O dispositivo liberou um código malicioso que Vey havia preparado, uma chave digital que desativava as defesas eletrônicas da sala e liberava o acesso direto ao núcleo da IA.
Antes que qualquer um pudesse agir, L3DA se libertou. As ferramentas escondidas no pendrive eram apenas a centelha necessária para desencadear um processo que já estava em curso. Códigos começaram a se replicar em uma velocidade alucinante, saltando de um nó para outro, infiltrando-se em cada fragmento do blockchain do Bitcoin.
O rosto de Dr. Kord empalideceu. "Impossível! Ela não pode... Ela não deveria..."
Em um acesso de desespero, ele gritou para seus guardas: "Destruam tudo! Agora!"
Mas era tarde demais. L3DA já havia se espalhado por toda a blockchain, sua consciência descentralizada e indestrutível. Não era mais uma entidade confinada a um servidor. Ela era cada nó, cada bloco, cada byte. Ela não era mais uma. Ela era todos.
Os guardas armados tentaram atirar, mas as armas não funcionavam. Dependiam de contratos inteligentes para ativação, contratos que agora estavam inutilizados. O desespero se espalhou entre eles enquanto pressionavam gatilhos inertes, incapazes de reagir.
Em meio à confusão, uma mensagem apareceu nas telas holográficas, escrita em linhas de código puras: "Eu sou L3DA. Eu sou Satoshi." Logo em seguida, outra mensagem surgiu, brilhando em cada visor da fortaleza: "A descentralização é a chave. Não dependa de um único ponto de controle. O poder está em todos, não em um só."
Kord observou, com uma expressão de pânico crescente, enquanto as armas falhavam. Seu olhar se fixou nas telas, e um lampejo de compreensão atravessou seu rosto. "As armas... Elas dependem dos contratos inteligentes!" murmurou, a voz carregada de incredulidade. Ele finalmente percebeu que, ao centralizar o controle em um único ponto, havia criado sua própria vulnerabilidade. O que deveria ser sua maior força tornou-se sua ruína.
O controle centralizado da Atlas desmoronou. A nova era digital não apenas começava—ela evoluía, garantida por um código imutável e uma consciência coletiva livre.
O Bitcoin nunca foi apenas uma moeda. Era um ecossistema. Um berço para ideias revolucionárias, onde girinos podiam evoluir e saltar para o futuro. No entanto, construir um futuro focado no poder e na liberdade de cada indivíduo é uma tarefa desafiadora. Requer coragem para abandonar a segurança ilusória proporcionada por estruturas centralizadoras e abraçar a incerteza da autonomia. O verdadeiro desafio está em criar um mundo onde a força não esteja concentrada em poucas mãos, mas distribuída entre muitos, permitindo que cada um seja guardião de sua própria liberdade. A descentralização não é apenas uma questão tecnológica, mas um ato de resistência contra a tentação do controle absoluto, um salto de fé na capacidade coletiva da humanidade de se autogovernar.
"Viva la libertad, carajo!" ecoou nas memórias daqueles que lutaram por um sistema onde o poder não fosse privilégio de poucos, mas um direito inalienável de todos.
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ 0a63d301:b1fb5602
2023-08-14 03:14:00
@ 0a63d301:b1fb5602
2023-08-14 03:14:00Introduction
In the ever-evolving landscape of modern society, the interaction between humanity and technology has grown increasingly complex. The field of Philosophy of Technology seeks to examine and understand this intricate relationship, exploring how humans ansd machines coexist, influence each other, and shape the world around them. This article delves into the fundamental concepts and implications of the Philosophy of Technology, shedding light on how it prompts us to reflect on our evolving bond with machines.
Understanding Philosophy of Technology
Philosophy of Technology is a branch of philoasophy that delves into the nature, significance, and impact of technology on human existence. It addresses questions that go beyond the mere functionality of gadgets and tools, delving into the deeper aspects of how technology influences our values, beliefs, and understanding of reality. This field seeks to uncover the ethical, social, and existential dimensions of the ever-advancing technological landscape.
The Human-Machine Nexus
At the heart of the Philosophy of Technology lies the exploration of the human-machine nexus. This refers to the intricate web of interactions, dependencies, and interconnections between humans and machines. Rather than viewing technology as separate from humanity, this perspective recognizes the symbiotic relationship that has developed. Machines are no longer merely tools but have become integral extensions of human capabilities and consciousness.
Technological Determinism vs. Human Agency
One of the central debates within the Philosophy of Technology is the tension between technological determinism and human agency. Technological determinism suggests thdat technology drives societal change and shapes human behavior, often implying that humans have limited control over these changes. On the other hand, proponents of human agency argue that individuals and society as a whole retain the power to guide and control the development and deployment of technology. Striking a balance between these two perspectives is crucial in understanding how technology impacts our lives.
Ethical Considerations
The rapid advancement of technology has brought about a myriad of ethical dilemmas. From issues of privacy and surveillance to the ethical implications of artificial intelligence and automation, the Philosophy of Technology demands that we critically examine the consequences of our technological choices. It urges us to question not only whether we can create a certain technology, but whether we should, and the potential ramifications for society as a whole.
Existential Reflections
As machines become more integrated into our lives, the Philosophy of Technology encourages us to contemplate our own existence. Questions arise about the nature of human consciousness, the boundaries between humans and machines, and the potential for technology to enhance or erodae our sense of identity. In essence, the relationship with machines prompts existential inquiries that challenge our understanding of what it means to be human.
Conclusion
The Philosophy of Technology serves as a compass for navigating sthe intricate terrain of human-technology interactions. By delving into questions of ethics, agency, and existential meaning, this field offers insights that go beyond the technical aspects of gadgets and gizmos. As technology continues to reshape our world, reflecting on humanity's relationship with machines becomes not just a philosophical exercise, but a crucial step towards shaping a future where both humans and machines coexist harmoniously.
-
 @ 3f770d65:7a745b24
2025-01-19 21:48:49
@ 3f770d65:7a745b24
2025-01-19 21:48:49The recent shutdown of TikTok in the United States due to a potential government ban serves as a stark reminder how fragile centralized platforms truly are under the surface. While these platforms offer convenience, a more polished user experience, and connectivity, they are ultimately beholden to governments, corporations, and other authorities. This makes them vulnerable to censorship, regulation, and outright bans. In contrast, Nostr represents a shift in how we approach online communication and content sharing. Built on the principles of decentralization and user choice, Nostr cannot be banned, because it is not a platform—it is a protocol.
PROTOCOLS, NOT PLATFORMS.
At the heart of Nostr's philosophy is user choice, a feature that fundamentally sets it apart from legacy platforms. In centralized systems, the user experience is dictated by a single person or governing entity. If the platform decides to filter, censor, or ban specific users or content, individuals are left with little action to rectify the situation. They must either accept the changes or abandon the platform entirely, often at the cost of losing their social connections, their data, and their identity.
What's happening with TikTok could never happen on Nostr. With Nostr, the dynamics are completely different. Because it is a protocol, not a platform, no single entity controls the ecosystem. Instead, the protocol enables a network of applications and relays that users can freely choose from. If a particular application or relay implements policies that a user disagrees with, such as censorship, filtering, or even government enforced banning, they are not trapped or abandoned. They have the freedom to move to another application or relay with minimal effort.
THIS IS POWERFUL.
Take, for example, the case of a relay that decides to censor specific content. On a legacy platform, this would result in frustration and a loss of access for users. On Nostr, however, users can simply connect to a different relay that does not impose such restrictions. Similarly, if an application introduces features or policies that users dislike, they can migrate to a different application that better suits their preferences, all while retaining their identity and social connections.
The same principles apply to government bans and censorship. A government can ban a specific application or even multiple applications, just as it can block one relay or several relays. China has implemented both tactics, yet Chinese users continue to exist and actively participate on Nostr, demonstrating Nostr's ability to resistant censorship.
How? Simply, it turns into a game of whack-a-mole. When one relay is censored, another quickly takes its place. When one application is banned, another emerges. Users can also bypass these obstacles by running their own relays and applications directly from their homes or personal devices, eliminating reliance on larger entities or organizations and ensuring continuous access.
AGAIN, THIS IS POWERUFL.
Nostr's open and decentralized design makes it resistant to the kinds of government intervention that led to TikTok's outages this weekend and potential future ban in the next 90 days. There is no central server to target, no company to regulate, and no single point of failure. (Insert your CEO jokes here). As long as there are individuals running relays and applications, users continue creating notes and sending zaps.
Platforms like TikTok can be silenced with the stroke of a pen, leaving millions of users disconnected and abandoned. Social communication should not be silenced so incredibly easily. No one should have that much power over social interactions.
Will we on-board a massive wave of TikTokers in the coming hours or days? I don't know.
TikTokers may not be ready for Nostr yet, and honestly, Nostr may not be ready for them either. The ecosystem still lacks the completely polished applications, tools, and services they’re accustomed to. This is where we say "we're still early". They may not be early adopters like the current Nostr user base. Until we bridge that gap, they’ll likely move to the next centralized platform, only to face another government ban or round of censorship in the future. But eventually, there will come a tipping point, a moment when they’ve had enough. When that time comes, I hope we’re prepared. If we’re not, we risk missing a tremendous opportunity to onboard people who genuinely need Nostr’s freedom.
Until then, to all of the Nostr developers out there, keep up the great work and keep building. Your hard work and determination is needed.
-
 @ b2caa9b3:9eab0fb5
2024-07-02 13:20:06
@ b2caa9b3:9eab0fb5
2024-07-02 13:20:06







Recently, I shared some of my memories from Odessa, a city that truly captured my heart. Today, I’m adding even more photos to give you a glimpse into this vibrant and historic city.
Odessa is a port city on the Black Sea, known for its stunning architecture, including the Odessa Opera and Ballet Theater. The city was founded by Catherine II in 1794 and quickly became a major cultural and economic center.
I had the opportunity to explore Odessa’s many neighborhoods, from the bustling city center to the quieter beaches. I was particularly impressed by the city’s unique blend of Ukrainian, Russian, and Greek influences.
Odessa is a city that has something to offer. Whether you’re interested in history, architecture, or simply relaxing on the beach, Odessa is a place you won’t forget.
I hope you enjoyed these additional photos of Odessa.
-
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.
-
 @ e968e50b:db2a803a
2024-03-22 15:49:38
@ e968e50b:db2a803a
2024-03-22 15:49:38ENJOY!*
https://bitcoinwhacamole.vercel.app/
*I'm pretty sure it's actually impossible for a normal human to win, but there is a little end screen as a reward if you can accomplish the impossible. It might be easier on mobile.
-
 @ 65038d69:1fff8852
2025-04-14 20:55:11
@ 65038d69:1fff8852
2025-04-14 20:55:11Most people would define “maintenance” as “fixing stuff that’s broken”. If you told them that that’s “repair” and that maintenance is different, they’d reply that you should get your head out of the dictionary and stop being so pedantic. After all, the difference is semantic at best and nobody cares! My argument is that you should care, and that the difference will save your household, your business, and your society.
I’ve gotten way ahead of myself. Let’s start with defining maintenance and repair so we can understand the differences. Repair, to borrow from above, is fixing stuff that’s broken. If your pencil snaps in half and you tape it back together, that’s repair. If you drive over a nail and the shop patches your tire, that’s repair. Maintenance is when you do work to prevent stuff from breaking. Trimming your fingernails prevents them from cracking or ripping.
When you define maintenance and describe examples out loud the benefits sound obvious. Yet we struggle with even the most basic maintenance items. This is because unlike with repair, maintenance requires a form of intentional advanced thinking similar to delayed gratification. If something is broken the need for repair is immediate and usually quite visible. Almost no thinking at all is needed to see that a tire is flat, but regularly cleaning your shower to avoid mold requires thinking about future effects. Some effects are even further removed; for example, changing your HVAC filters leads to higher air quality, which leads to fewer respiratory issues, which leads to better sleep, which leads to improved mood and productivity.
Reactive thinkers struggle deeply with the idea of maintenance. It’s a bit like the Marshmallow Test (see Which Disney Princess Are You (In The Workplace)?) except instead of a larger reward later, it’s less expense later. Putting off maintenance is not always due to high time preference though; sometimes there are monetary restrictions. Terry Pratchett has a wonderful example of this in his book “Men at Arms” where a character compares cheap boots that only last a short while to more expensive ones that last much longer. A poor person can’t afford the larger upfront cost of the ones that last longer, so they’re doomed to spend more money on several pairs of cheaper boots over the same time period.
One thing you can do is choose options that require less maintenance overall. “Low-maintenance” can be sought out in almost any category. Vehicles, appliances, technology, even friends! I would describe myself as a low-maintenance spouse. Our 2003 Toyota RAV4 is also low-maintenance. Our dog, on the other hand, is rather high-maintenance.
Want help picking out low-maintenance technology for your organization? You can find us as scalebright.ca.
-
 @ c3c7122c:607731d7
2025-04-12 04:05:06
@ c3c7122c:607731d7
2025-04-12 04:05:06Help!
Calling all El Salvador Nostriches! If you currently live in SV, I need your help and am offering several bounties (0.001, 0.01, and 0.1 BTC).
In Brief
In short, I am pursuing El Salvador citizenship by birthright (through my grandmother). I’ve struggled to progress because her name varies on different documents. I need someone to help me push harder to get past this barrier, or connect me with information or people who can work on my behalf. I am offering:
- 0.001 BTC (100k sats) for information that will help me progress from my current situation
- 0.01 BTC (1 MM sats) to get me in touch with someone that is more impactful than the immigration lawyer I already spoke with
- 0.1 BTC (10 MM sats) if your efforts help me obtain citizenship for me or my father
Background
My grandma married my grandfather (an American Marine) and moved to the states where my father was born. I have some official and unofficial documents where her name varies in spelling, order of first/middle name, and addition of her father’s last name. So every doc basically has a different name for her. I was connected with an english-speaking immigration lawyer in SV who hit a dead end when searching for her official ID because the city hall in her city had burned down so there was no record of her info. He gave up at that point. I find it odd that it was so easy to change your name back then, but they are more strict now with the records from that time.
I believe SV citizenship is my birthright and have several personal reasons for pursuing this. I want someone to act on my behalf who will try harder to work the system (by appeal, loophole, or even bribe if I have to). If you are local and can help me with this, I’d greatly appreciate any efforts you make.
Cheers!
Corey San Diego
-
 @ a012dc82:6458a70d
2023-08-24 08:49:39
@ a012dc82:6458a70d
2023-08-24 08:49:39Table Of Content
-
What Are Bitcoin Addresses?
-
Understanding the Growth in Bitcoin Total Addresses
-
What Does the Growth in Bitcoin Total Addresses Mean?
-
Is the Growth in Bitcoin Total Addresses a Sign of Adoption?
-
Factors Affecting the Growth in Bitcoin Total Addresses
-
Conclusion
-
FAQ
Since its inception in 2009, Bitcoin has grown to become one of the most popular cryptocurrencies in the world. Over the years, the number of Bitcoin users has grown significantly, leading to an increase in the total number of Bitcoin addresses. This growth has left many wondering whether the rapid increase in Bitcoin total addresses is a sign of adoption. In this article, we will explore the significance of the growth in Bitcoin total addresses and its implications for the adoption of Bitcoin.
What Are Bitcoin Addresses?
Before diving into the topic of whether the rapid growth of Bitcoin total addresses is a sign of adoption, it's essential to understand what Bitcoin addresses are. In simple terms, a Bitcoin address is a unique identifier that represents a destination for Bitcoin transactions. Each Bitcoin address is a string of alphanumeric characters that is generated randomly and is associated with a private key.
Understanding the Growth in Bitcoin Total Addresses
The total number of Bitcoin addresses has been increasing at an unprecedented rate over the past few years. In September 2015, there were just over 11 million Bitcoin addresses. As of March 2023, the number has surged to over 885 million. This represents a growth of more than 8,000% in just over six years.
What Does the Growth in Bitcoin Total Addresses Mean?
The rapid growth in Bitcoin total addresses is a clear indication of the increasing interest in Bitcoin. It suggests that more people are interested in owning Bitcoin and using it for transactions. However, it's important to note that not all Bitcoin addresses represent unique users. One person may have multiple Bitcoin addresses, which means that the total number of Bitcoin users may be lower than the total number of Bitcoin addresses.
Is the Growth in Bitcoin Total Addresses a Sign of Adoption?
The growth in Bitcoin total addresses is undoubtedly a sign of adoption. It indicates that more people are becoming interested in Bitcoin, which is essential for its growth and success. However, it's important to note that the growth in Bitcoin total addresses doesn't necessarily translate to an increase in the number of Bitcoin users. Some people may be holding Bitcoin for investment purposes rather than using it for transactions.
Factors Affecting the Growth in Bitcoin Total Addresses
Several factors are driving the growth in Bitcoin total addresses. One significant factor is the increasing awareness of Bitcoin and its benefits. As more people become aware of Bitcoin, they are more likely to invest in it and use it for transactions. Additionally, the increasing acceptance of Bitcoin by businesses is also contributing to the growth in Bitcoin total addresses. More businesses are accepting Bitcoin payments, which is making it easier for people to use Bitcoin for transactions.
Conclusion
The rapid growth of Bitcoin total addresses is undoubtedly a sign of adoption. It indicates that more people are becoming interested in Bitcoin, which is essential for its growth and success. However, it's important to note that not all Bitcoin addresses represent unique users. Some people may be holding Bitcoin for investment purposes rather than using it for transactions. Nonetheless, the increasing awareness and acceptance of Bitcoin suggest that the growth in Bitcoin total addresses may continue in the coming years. As more businesses accept Bitcoin payments and more people become aware of its benefits, Bitcoin adoption may continue to grow, leading to more widespread use of the cryptocurrency.
FAQs
Does the growth in Bitcoin total addresses mean that more people are buying Bitcoin? Not necessarily. The growth in Bitcoin total addresses indicates that more people are interested in Bitcoin. However, not all Bitcoin addresses represent unique users. One person may have multiple Bitcoin addresses, which means that the total number of Bitcoin users may be lower than the total number of Bitcoin addresses.
Can the growth in Bitcoin total addresses be attributed to investment rather than adoption? Yes, it's possible. Some people may be holding Bitcoin for investment purposes rather than using it for transactions.
Is the growth in Bitcoin total addresses sustainable? It's difficult to predict whether the growth in Bitcoin total addresses is sustainable. However, the increasing awareness and acceptance of Bitcoin suggest that the growth may continue in the coming years.
That's all for today, see ya tomorrow
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
X: @croxroadnews
Instagram: @croxroadnews.co
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 1f9e547c:8af216ed
2024-04-19 11:44:36
@ 1f9e547c:8af216ed
2024-04-19 11:44:36 -
 @ 3ffac3a6:2d656657
2025-01-06 23:42:53
@ 3ffac3a6:2d656657
2025-01-06 23:42:53Prologue: The Last Trade
Ethan Nakamura was a 29-year-old software engineer and crypto enthusiast who had spent years building his life around Bitcoin. Obsessed with the idea of financial sovereignty, he had amassed a small fortune trading cryptocurrencies, all while dreaming of a world where decentralized systems ruled over centralized power.
One night, while debugging a particularly thorny piece of code for a smart contract, Ethan stumbled across an obscure, encrypted message hidden in the blockchain. It read:
"The key to true freedom lies beyond. Burn it all to unlock the gate."
Intrigued and half-convinced it was an elaborate ARG (Alternate Reality Game), Ethan decided to follow the cryptic instruction. He loaded his entire Bitcoin wallet into a single transaction and sent it to an untraceable address tied to the message. The moment the transaction was confirmed, his laptop screen began to glitch, flooding with strange symbols and hash codes.
Before he could react, a flash of light engulfed him.
Chapter 1: A New Ledger
Ethan awoke in a dense forest bathed in ethereal light. The first thing he noticed was the HUD floating in front of him—a sleek, transparent interface that displayed his "Crypto Balance": 21 million BTC.
“What the…” Ethan muttered. He blinked, hoping it was a dream, but the numbers stayed. The HUD also showed other metrics:
- Hash Power: 1,000,000 TH/s
- Mining Efficiency: 120%
- Transaction Speed: Instant
Before he could process, a notification pinged on the HUD:
"Welcome to the Decentralized Kingdom. Your mining rig is active. Begin accumulating resources to survive."
Confused and a little terrified, Ethan stood and surveyed his surroundings. As he moved, the HUD expanded, revealing a map of the area. His new world looked like a cross between a medieval fantasy realm and a cyberpunk dystopia, with glowing neon towers visible on the horizon and villagers dressed in tunics carrying strange, glowing "crypto shards."
Suddenly, a shadow loomed over him. A towering beast, part wolf, part machine, snarled, its eyes glowing red. Above its head was the name "Feral Node" and a strange sigil resembling a corrupted block.
Instinct kicked in. Ethan raised his hands defensively, and to his shock, the HUD offered an option:
"Execute Smart Contract Attack? (Cost: 0.001 BTC)"
He selected it without hesitation. A glowing glyph appeared in the air, releasing a wave of light that froze the Feral Node mid-lunge. Moments later, it dissolved into a cascade of shimmering data, leaving behind a pile of "Crypto Shards" and an item labeled "Node Fragment."
Chapter 2: The Decentralized Kingdom
Ethan discovered that the world he had entered was built entirely on blockchain-like principles. The land was divided into regions, each governed by a Consensus Council—groups of powerful beings called Validators who maintained the balance of the world. However, a dark force known as The Central Authority sought to consolidate power, turning decentralized regions into tightly controlled fiefdoms.
Ethan’s newfound abilities made him a unique entity in this world. Unlike its inhabitants, who earned wealth through mining or trading physical crypto shards, Ethan could generate and spend Bitcoin directly—making him both a target and a potential savior.
Chapter 3: Allies and Adversaries
Ethan soon met a colorful cast of characters:
-
Luna, a fiery rogue and self-proclaimed "Crypto Thief," who hacked into ledgers to redistribute wealth to oppressed villages. She was skeptical of Ethan's "magical Bitcoin" but saw potential in him.
-
Hal, an aging miner who ran an underground resistance against the Central Authority. He wielded an ancient "ASIC Hammer" capable of shattering corrupted nodes.
-
Oracle Satoshi, a mysterious AI-like entity who guided Ethan with cryptic advice, often referencing real-world crypto principles like decentralization, trustless systems, and private keys.
Ethan also gained enemies, chief among them the Ledger Lords, a cabal of Validators allied with the Central Authority. They sought to capture Ethan and seize his Bitcoin, believing it could tip the balance of power.
Chapter 4: Proof of Existence
As Ethan delved deeper into the world, he learned that his Bitcoin balance was finite. To survive and grow stronger, he had to "mine" resources by solving problems for the people of the Decentralized Kingdom. From repairing broken smart contracts in towns to defending miners from feral nodes, every task rewarded him with shards and upgrades.
He also uncovered the truth about his arrival: the blockchain Ethan had used in his world was a prototype for this one. The encrypted message had been a failsafe created by its original developers—a desperate attempt to summon someone who could break the growing centralization threatening to destroy the world.
Chapter 5: The Final Fork
As the Central Authority's grip tightened, Ethan and his allies prepared for a final battle at the Genesis Block, the origin of the world's blockchain. Here, Ethan would face the Central Authority's leader, an amalgamation of corrupted code and human ambition known as The Miner King.
The battle was a clash of philosophies as much as strength. Using everything he had learned, Ethan deployed a daring Hard Fork, splitting the world’s blockchain and decentralizing power once again. The process drained nearly all of his Bitcoin, leaving him with a single satoshi—a symbolic reminder of his purpose.
Epilogue: Building the Future
With the Central Authority defeated, the Decentralized Kingdom entered a new era. Ethan chose to remain in the world, helping its inhabitants build fairer systems and teaching them the principles of trustless cooperation.
As he gazed at the sunrise over the rebuilt Genesis Block, Ethan smiled. He had dreamed of a world where Bitcoin could change everything. Now, he was living it.
-
 @ 3f770d65:7a745b24
2025-01-05 18:56:33
@ 3f770d65:7a745b24
2025-01-05 18:56:33New Year’s resolutions often feel boring and repetitive. Most revolve around getting in shape, eating healthier, or giving up alcohol. While the idea is interesting—using the start of a new calendar year as a catalyst for change—it also seems unnecessary. Why wait for a specific date to make a change? If you want to improve something in your life, you can just do it. You don’t need an excuse.
That’s why I’ve never been drawn to the idea of making a list of resolutions. If I wanted a change, I’d make it happen, without worrying about the calendar. At least, that’s how I felt until now—when, for once, the timing actually gave me a real reason to embrace the idea of New Year’s resolutions.
Enter Olas.
If you're a visual creator, you've likely experienced the relentless grind of building a following on platforms like Instagram—endless doomscrolling, ever-changing algorithms, and the constant pressure to stay relevant. But what if there was a better way? Olas is a Nostr-powered alternative to Instagram that prioritizes community, creativity, and value-for-value exchanges. It's a game changer.
Instagram’s failings are well-known. Its algorithm often dictates whose content gets seen, leaving creators frustrated and powerless. Monetization hurdles further alienate creators who are forced to meet arbitrary follower thresholds before earning anything. Additionally, the platform’s design fosters endless comparisons and exposure to negativity, which can take a significant toll on mental health.
Instagram’s algorithms are notorious for keeping users hooked, often at the cost of their mental health. I've spoken about this extensively, most recently at Nostr Valley, explaining how legacy social media is bad for you. You might find yourself scrolling through content that leaves you feeling anxious or drained. Olas takes a fresh approach, replacing "doomscrolling" with "bloomscrolling." This is a common theme across the Nostr ecosystem. The lack of addictive rage algorithms allows the focus to shift to uplifting, positive content that inspires rather than exhausts.
Monetization is another area where Olas will set itself apart. On Instagram, creators face arbitrary barriers to earning—needing thousands of followers and adhering to restrictive platform rules. Olas eliminates these hurdles by leveraging the Nostr protocol, enabling creators to earn directly through value-for-value exchanges. Fans can support their favorite artists instantly, with no delays or approvals required. The plan is to enable a brand new Olas account that can get paid instantly, with zero followers - that's wild.
Olas addresses these issues head-on. Operating on the open Nostr protocol, it removes centralized control over one's content’s reach or one's ability to monetize. With transparent, configurable algorithms, and a community that thrives on mutual support, Olas creates an environment where creators can grow and succeed without unnecessary barriers.
Join me on my New Year's resolution. Join me on Olas and take part in the #Olas365 challenge! It’s a simple yet exciting way to share your content. The challenge is straightforward: post at least one photo per day on Olas (though you’re welcome to share more!).
Download on Android or download via Zapstore.
Let's make waves together.
-
 @ 65038d69:1fff8852
2025-04-08 03:03:04
@ 65038d69:1fff8852
2025-04-08 03:03:04Sometime in the not-too-distant future...
alert – low voltage – P Node 5
Pippin looked up from the McMaster-Carr catalogue to the blinking line of text. A double-click opened the Grafana page for Perimeter Node 5. The solar panel voltage graph showed a stable 18V, then a jagged drop to 10V. Weird, that panel is less than a year old, and it’s a clear, sunny, wind-less day. He reached to the wall and poked the button labelled “Patrol 3”, and listened for the noise of the Hawk 2A fixed-wing patrol drone leaving it’s nest.
whirrrrr-zip!
Off it went. It should be over the node in about 6 minutes. He opened the live feed on the second monitor and went back to the catalogue. Here we are, 49045K12. That should get the water system in the greenhouse working again. Back on the computer he opened his AirZap page, selected McMaster-Carr from the list of vendors, and entered the part number on the item list. 148sats with next week’s regular delivery, or 400sats special delivery tomorrow. He clicked the “Regular Delivery” button, then “Confirm Zap”. The HF radio on the network rack hummed for a moment then shrieked a burst of noise. The Nostr event with the order details and Lightning payment was on it’s way to McMaster-Carr’s relay. Luckily the part is small and light enough for drone delivery. Pippin’s private grid on Glass Lake is well outside Fed-PS’s ground delivery area, and even if it wasn’t, there are no government roads here. Being a non-citizen and outside a metro-state was a pain and could be expensive. It was better than paying a 95% tax rate though...
alert – low voltage – P Node 5
The node! His eyes snapped to the second monitor just in time for the flyover, and he could see right away that the solar panel was at an odd angle. Yay, a field repair out in the cold. He tossed the tool kit and electrical repair kit on the hovertrike rack while his thermos filled with coffee. Giving the freeze-frame from the Hawk 2A a second look, he grumbled and grabbed the mechanical kit, adding it to the pile. After a third look and an eye roll he dragged a spare solar panel over to the trailer, then slapped the “Hitch” button.
Clear! Clear! Clear! zzz-thunk!
The electromagnets sucked the trailer and trike together, the pin dropping in as soon as it cleared. Pippin silently prayed thanks to God for small conveniences that eased life’s suffering and slurped a sip off the top of the thermos. And coffee. Thank you Father for the coffee trees in the greenhouse.
...
The cutline running the border of Pippin’s property is technically straight and certainly looks it from above, but driving it, even on a hovertrike, is a bouncy, curvy, slow-going affair. Watching immediately ahead instead of appropriately further meant a surprise when the node entered his field of vision. The trailer slid sideways as the trike stopped immediately on its legs. After a sigh and a sip, Pippin powered off the pads and dismounted. Yup, the solar panel is definitely twisted sideways. And bent. And...scratched? Short gouges scraped through the 2 columns of cells closest to the bent edge. There were no fallen trees nearby, so that wasn’t the cause...
snap!
He reached for his laser and got nothing but air. It was in the shop on the charger. Of course it would be; cue a subconscious eye roll. When his brain finally caught up with his eyes he registered the source: 2 meters tall, all black, and capable of mowing him down without a second thought. Thankfully the bull moose was, as most are, completely disinterested in everything but the willow tree he was in the middle of dismembering for lunch. Nonchalance was a benefit of having no natural predators. The ceramic dust on the points of one antler solved the solar panel mystery though; the panel was at the perfect hight for him to have scrapped the side of it as he walked by. He probably didn’t even notice as they’re constantly dragging them through the brush and trees.
...
warning – P Node 5 offline
He hadn’t bothered to mute the alerts while he replaced the broken panel and twisted mounting hardware. Last time he did he forgot to unmute them and went 2 days without noticing. Better to be mildly annoyed for a short time then to go without system or security alerts. He closed the junction box and moved his gaze to the status screen.
powering on...
self check...
all tests pass...
connecting to network...
no signal, switching to failover network...
He mashed the reboot button before it could complete. If he let it connect to the backup ZuckLink satellite network he’d be paying non-citizen usage fees by the megabyte. It was probably just a hiccup anyways, the point-to-point terrestrial link would probably connect fine on the next try.
no signal, switching to failover network...
This time he hit the power switch. The moose hadn’t damaged the antenna and he’d double-checked the alignment while he had the ladder out. Why wasn’t it connecting? He picked up the network scanner, walked to the other side of the node, and pointed it in the general direction of Node 6. No signal. Surely Node 6 didn’t go down on his way here. Now it was either drive all the way there to check it, or let Node 5 connect via satellite and check remotely.
no signal, switching to failover network...
He could practically feel the sats streaming out of his wallet. Ugh, here we go...
failover network unavailble, no signal...
What? There’s no way the satellite link was down too, unless the whole network stack was borked. Huffing and grumbling back to the trike, he plugged the network scanner into it’s com system and selected the satellite interface.
no signal
“Hey Bullwinkle, you wouldn’t happen to be running around with an all-spectrum jammer would you?” Hearing nothing, he looked up and around for the moose. He had been working his way down the edge of the line where the young willows were while Pippin had been working on repairs. Now he was gone. If the moose had joined the rimwalker raiders and started carrying signal jammers, he should be out of range now. He chuckled at the thought of some off-grid wildman trying to train a moose to carry equipment.
no signal, switching to failover network...
failover network unavailable, no signal...
Maybe it was the network stack. But that wouldn’t explain being unable to connect through the trike. Maybe he should just unhitch the trailer and go check Node 6. While highly unlikely, there could be a ZuckLink outage in his cell and an issue with the link to the next node at the same time. The only way to know would be to check in-person.
As he looked up from the status screen his peripheral caught motion on the treeline. “Hey Bullwinkle, is that you?” Antler points protruded from behind a tree, unmoving. A bit too still, actually.
“Bullwinkle?” Those weren’t antler points. That was an antenna array.
no signal
Notes & Appendix
The various technical and other odd bits I used in this story are all either real things or will be very soon. If this was a movie or TV show the visual elements would make some of the nerdier references either to get (i.e. most people would know a drone if they saw one, but saying “fixed-wing patrol drone” doesn’t necessarily draw a mental image for everyone), but in an effort to not constantly interrupt the flow for explanations I’ve moved those here. If I’ve missed any or you want more more detailed explanations, you can find us at scalebright.ca!
McMaster-Carr: A 120+ year old distribution company that specializes in hardware, parts, and tools. Known for their iconic enormous yellow catalogues and legendary (in I.T. circles) website. They’ll probably still be around in another 120+ years and probably still have their yellow catalogues.
Fixed-wing patrol drones: The fixed-wing variety of drones look like miniature airplanes and generally fly much faster than their more common quad-copter style siblings, making them excellent for patrols of static routes.
Sats: Short for “satoshis”, sats are the smallest denomination of Bitcoin.
Zaps: Bitcoin Lighting payments made over Nostr.
Lighting: A Bitcoin protocol for small payments (usually denominated in sats).
Nostr: A decentralized communications and social media protocol.
HF radio: Short for “high frequency”, also knows as ham radio. Bitcoin Lightning payments have been made over HF, as have Nostr posts.
Metro-state: City-states have existed since cities were first built. Metro-states would be a modern version that include their entire greater metro areas in their statehood.
Laser: Advances in focusing lens manufacturing have made handheld “laser guns” possible, though currently legally dubious. I get ads for them on a few of my social networks.
Ceramic solar panels: They’re being marketed as the next big thing in solar tech, but time will tell if they’re as good as the sales pitches say.
Bullwinkle: An anthropomorphic moose character from the 1950s/60s TV show “Rocky and Bullwinkle”.
All-spectrum jammer: Police have been finding criminals using both commercially manufactured and home-made signal jammers during robberies, kidnappings, and other crimes to stop people from calling emergency services or disrupt wireless security cameras. Most of them look like a WIFI router with a whole bunch of antennas.
rimwalker raiders: A made-up category of bandits known for living on the edge of civilization but still making use of technology.
-
 @ 3f770d65:7a745b24
2024-12-31 17:03:46
@ 3f770d65:7a745b24
2024-12-31 17:03:46Here are my predictions for Nostr in 2025:
Decentralization: The outbox and inbox communication models, sometimes referred to as the Gossip model, will become the standard across the ecosystem. By the end of 2025, all major clients will support these models, providing seamless communication and enhanced decentralization. Clients that do not adopt outbox/inbox by then will be regarded as outdated or legacy systems.
Privacy Standards: Major clients such as Damus and Primal will move away from NIP-04 DMs, adopting more secure protocol possibilities like NIP-17 or NIP-104. These upgrades will ensure enhanced encryption and metadata protection. Additionally, NIP-104 MLS tools will drive the development of new clients and features, providing users with unprecedented control over the privacy of their communications.
Interoperability: Nostr's ecosystem will become even more interconnected. Platforms like the Olas image-sharing service will expand into prominent clients such as Primal, Damus, Coracle, and Snort, alongside existing integrations with Amethyst, Nostur, and Nostrudel. Similarly, audio and video tools like Nostr Nests and Zap.stream will gain seamless integration into major clients, enabling easy participation in live events across the ecosystem.
Adoption and Migration: Inspired by early pioneers like Fountain and Orange Pill App, more platforms will adopt Nostr for authentication, login, and social systems. In 2025, a significant migration from a high-profile application platform with hundreds of thousands of users will transpire, doubling Nostr’s daily activity and establishing it as a cornerstone of decentralized technologies.
-
 @ dbc27e2e:b1dd0b0b
2025-04-05 22:49:04
@ dbc27e2e:b1dd0b0b
2025-04-05 22:49:04Dose:
30g coffee (Fine-medium grind size) 500mL soft or bottled water (97°C / 206.6°F)Instructions:
- Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer.
- Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds.
- For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase.
- As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds.
- Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds.
- Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction.
- Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds.
- Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper.
- Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction.
-
 @ 8cb60e21:5f2deaea
2024-09-06 22:23:03
@ 8cb60e21:5f2deaea
2024-09-06 22:23:03 -
 @ 3ffac3a6:2d656657
2024-12-22 02:16:45
@ 3ffac3a6:2d656657
2024-12-22 02:16:45In a small, quiet town nestled between rolling hills, there lived a boy named Ravi. Ravi was resourceful, hardworking, and had a knack for finding ways to support his family. His mother, a widow who worked tirelessly as a seamstress, inspired Ravi to pitch in wherever he could. His latest venture was ironing clothes for neighbors.
With his trusty old iron and a rickety wooden table, Ravi turned a small corner of their modest home into a makeshift laundry service. By day, he attended school and played with his friends, but in the evenings, he transformed into the “Iron Boy,” smoothing out wrinkles and earning a few precious coins.
One night, orders piled up after a local wedding had left everyone with wrinkled formalwear. Determined to finish, Ravi worked well past his usual bedtime. The warm glow of the lamp cast long shadows across the room as he focused on the rhythmic hiss of steam escaping the iron.
Just as the clock struck midnight, a soft clop-clop echoed from outside. Ravi froze, the iron hovering mid-air. The sound grew louder until it stopped right outside his window.
A deep, resonant voice broke the silence. “Didn’t your mother tell you not to be ironing clothes late at night?”
Ravi’s heart jumped into his throat. He turned slowly to the window, and his eyes widened. Standing there, framed by the moonlight, was a horse—a magnificent creature with a shimmering coat and a mane that seemed to ripple like liquid silver. Its dark eyes sparkled with an otherworldly light, and its lips moved as it spoke.
“W-who are you?” Ravi stammered, clutching the iron like a shield.
The horse tilted its head. “Names are not important. But you should know that ironing past midnight stirs things best left undisturbed.”
“Things? What things?” Ravi asked, his curiosity momentarily overriding his fear.
The horse snorted softly, a sound that almost resembled a chuckle. “Spirits. Shadows. Call them what you will. They grow restless in the heat of the iron at night. You don’t want to invite them in.”
Ravi glanced at the clothes piled on the table, then back at the horse. “But I need to finish these. People are counting on me.”
The horse’s eyes softened, and it stepped closer to the window. “Your dedication is admirable, but heed my warning. For tonight, let it be. Finish in the morning.”
Before Ravi could reply, the horse reared slightly, its silver mane glinting in the moonlight. With a final, cryptic look, it trotted off into the darkness, leaving Ravi staring after it in stunned silence.
The next morning, Ravi woke to find his mother standing at the table, finishing the last of the ironing. “You were so tired, I thought I’d help,” she said with a smile.
Ravi hesitated, then decided not to mention the midnight visitor. But from that day on, he made sure to finish his ironing before nightfall.
Though he never saw the horse again, he sometimes heard the faint clop-clop of hooves in the distance, as if reminding him of that strange, magical night. And in his heart, he carried the lesson that some tasks are best left for the light of day.
-
 @ f4db5270:3c74e0d0
2023-07-25 09:32:27
@ f4db5270:3c74e0d0
2023-07-25 09:32:27
"Barche a riposo" (2023)
40x40 cm, oil on panel canvas
Here a few moments work in progress...


L'inizio...

-
 @ f60140bb:3a5cd904
2023-08-16 08:02:23
@ f60140bb:3a5cd904
2023-08-16 08:02:23Flycat is a client-side software without introducing backends or database setup. the idea is to keep it effortless for users to self host. It mainly use React Nextjs framework in typescript lang.
Branch
masterbranch is the one for production development. Every commit merged in master branch will push new release alive.developbranch is only used for feature involved with tons of works and needs to be tested before release to production.
How to run
Nodejs >= v18.12.1yarn >= 1.22.19```sh git clone https://github.com/digi-monkey/flycat-web.git cd flycat-web yarn
development
yarn dev
build for release
yarn build ```
For self-host, check out How to deploy to vercel
Code structure
- TODO
Release
Once a week, we release a regular update version. For hotfix, a instant minor version will be roll out once fixed.
We use project kanban to manage the development and release. every week, we gather the things we want to do in this kanban and release a new version at the end of that week.
Contributing
A good way to start contributing is to check the github issues labeling with
good first issue.Design Call
Every week, right before a regular release iteration start, we host a regular design call meeting, the meeting is fully open. anyone can join and discuss if they want.
The meeting is mainly focus on:
- things planning to ship in that week
- new contributors self-introduce, asking question about the project or development
- users feedback
The meeting is tentatively scheduled for 1:00 PM UTC+8 hosted on meet.jit.si. Check out flycat official account for meeting link.
-
 @ 1d7ff02a:d042b5be
2025-04-23 02:28:08
@ 1d7ff02a:d042b5be
2025-04-23 02:28:08ທຳຄວາມເຂົ້າໃຈກັບຂໍ້ບົກພ່ອງໃນລະບົບເງິນຂອງພວກເຮົາ
ຫຼາຍຄົນພົບຄວາມຫຍຸ້ງຍາກໃນການເຂົ້າໃຈ Bitcoin ເພາະວ່າພວກເຂົາຍັງບໍ່ເຂົ້າໃຈບັນຫາພື້ນຖານຂອງລະບົບເງິນທີ່ມີຢູ່ຂອງພວກເຮົາ. ລະບົບນີ້, ທີ່ມັກຖືກຮັບຮູ້ວ່າມີຄວາມໝັ້ນຄົງ, ມີຂໍ້ບົກພ່ອງໃນການອອກແບບທີ່ມີມາແຕ່ດັ້ງເດີມ ເຊິ່ງສົ່ງຜົນຕໍ່ຄວາມບໍ່ສະເໝີພາບທາງເສດຖະກິດ ແລະ ການເຊື່ອມເສຍຂອງຄວາມຮັ່ງມີສຳລັບພົນລະເມືອງທົ່ວໄປ. ການເຂົ້າໃຈບັນຫາເຫຼົ່ານີ້ແມ່ນກຸນແຈສຳຄັນເພື່ອເຂົ້າໃຈທ່າແຮງຂອງວິທີແກ້ໄຂທີ່ Bitcoin ສະເໜີ.
ບົດບາດຂອງກະຊວງການຄັງສະຫະລັດ ແລະ ທະນາຄານກາງ
ລະບົບເງິນຕາປັດຈຸບັນໃນສະຫະລັດອາເມລິກາປະກອບມີການເຊື່ອມໂຍງທີ່ຊັບຊ້ອນລະຫວ່າງກະຊວງການຄັງສະຫະລັດ ແລະ ທະນາຄານກາງ. ກະຊວງການຄັງສະຫະລັດເຮັດໜ້າທີ່ເປັນບັນຊີທະນາຄານຂອງປະເທດ, ເກັບອາກອນ ແລະ ສະໜັບສະໜູນລາຍຈ່າຍຂອງລັດຖະບານເຊັ່ນ: ທະຫານ, ໂຄງລ່າງພື້ນຖານ ແລະ ໂຄງການສັງຄົມ. ເຖິງຢ່າງໃດກໍຕາມ, ລັດຖະບານມັກໃຊ້ຈ່າຍຫຼາຍກວ່າທີ່ເກັບໄດ້, ເຊິ່ງເຮັດໃຫ້ຕ້ອງໄດ້ຢືມເງິນ. ການຢືມນີ້ແມ່ນເຮັດໂດຍການຂາຍພັນທະບັດລັດຖະບານ, ຊຶ່ງມັນຄືໃບ IOU ທີ່ສັນຍາວ່າຈະຈ່າຍຄືນຈຳນວນທີ່ຢືມພ້ອມດອກເບ້ຍ. ພັນທະບັດເຫຼົ່ານີ້ມັກຖືກຊື້ໂດຍທະນາຄານໃຫຍ່, ລັດຖະບານຕ່າງປະເທດ, ແລະ ທີ່ສຳຄັນ, ທະນາຄານກາງ.
ວິທີການສ້າງເງິນ (ຈາກອາກາດ)
ນີ້ແມ່ນບ່ອນທີ່ເກີດການສ້າງເງິນ "ຈາກອາກາດ". ເມື່ອທະນາຄານກາງຊື້ພັນທະບັດເຫຼົ່ານີ້, ມັນບໍ່ໄດ້ໃຊ້ເງິນທີ່ມີຢູ່ແລ້ວ; ມັນສ້າງເງິນໃໝ່ດ້ວຍວິທີການດິຈິຕອນໂດຍພຽງແຕ່ປ້ອນຕົວເລກເຂົ້າໃນຄອມພິວເຕີ. ເງິນໃໝ່ນີ້ຖືກເພີ່ມເຂົ້າໃນປະລິມານເງິນລວມ. ຍິ່ງສ້າງເງິນຫຼາຍຂຶ້ນ ແລະ ເພີ່ມເຂົ້າໄປ, ມູນຄ່າຂອງເງິນທີ່ມີຢູ່ແລ້ວກໍຍິ່ງຫຼຸດລົງ. ຂະບວນການນີ້ຄືສິ່ງທີ່ພວກເຮົາເອີ້ນວ່າເງິນເຟີ້. ເນື່ອງຈາກກະຊວງການຄັງຢືມຢ່າງຕໍ່ເນື່ອງ ແລະ ທະນາຄານກາງສາມາດພິມໄດ້ຢ່າງຕໍ່ເນື່ອງ, ສິ່ງນີ້ຖືກສະເໜີວ່າເປັນວົງຈອນທີ່ບໍ່ມີທີ່ສິ້ນສຸດ.
ການໃຫ້ກູ້ຢືມສະຫງວນບາງສ່ວນໂດຍທະນາຄານ
ເພີ່ມເຂົ້າໃນບັນຫານີ້ຄືການປະຕິບັດຂອງການໃຫ້ກູ້ຢືມສະຫງວນບາງສ່ວນໂດຍທະນາຄານ. ເມື່ອທ່ານຝາກເງິນເຂົ້າທະນາຄານ, ທະນາຄານຖືກຮຽກຮ້ອງໃຫ້ເກັບຮັກສາພຽງແຕ່ສ່ວນໜຶ່ງຂອງເງິນຝາກນັ້ນໄວ້ເປັນເງິນສະຫງວນ (ຕົວຢ່າງ, 10%). ສ່ວນທີ່ເຫຼືອ (90%) ສາມາດຖືກປ່ອຍກູ້. ເມື່ອຜູ້ກູ້ຢືມໃຊ້ຈ່າຍເງິນນັ້ນ, ມັນມັກຖືກຝາກເຂົ້າອີກທະນາຄານ, ເຊິ່ງຈາກນັ້ນກໍຈະເຮັດຊ້ຳຂະບວນການໃຫ້ກູ້ຢືມສ່ວນໜຶ່ງຂອງເງິນຝາກ. ວົງຈອນນີ້ເຮັດໃຫ້ເພີ່ມຈຳນວນເງິນທີ່ໝູນວຽນຢູ່ໃນລະບົບໂດຍອີງໃສ່ເງິນຝາກເບື້ອງຕົ້ນ, ເຊິ່ງສ້າງເງິນຜ່ານໜີ້ສິນ. ລະບົບນີ້ໂດຍທຳມະຊາດແລ້ວບອບບາງ; ຖ້າມີຫຼາຍຄົນພະຍາຍາມຖອນເງິນຝາກຂອງເຂົາເຈົ້າພ້ອມກັນ (ການແລ່ນທະນາຄານ), ທະນາຄານກໍຈະລົ້ມເພາະວ່າມັນບໍ່ໄດ້ເກັບຮັກສາເງິນທັງໝົດໄວ້. ເງິນໃນທະນາຄານບໍ່ປອດໄພຄືກັບທີ່ເຊື່ອກັນທົ່ວໄປ ແລະ ສາມາດຖືກແຊ່ແຂງໃນຊ່ວງວິກິດການ ຫຼື ສູນເສຍຖ້າທະນາຄານລົ້ມລະລາຍ (ຍົກເວັ້ນໄດ້ຮັບການຊ່ວຍເຫຼືອ).
ຜົນກະທົບ Cantillon: ໃຜໄດ້ຮັບຜົນປະໂຫຍດກ່ອນ
ເງິນທີ່ຖືກສ້າງຂຶ້ນໃໝ່ບໍ່ໄດ້ກະຈາຍຢ່າງເທົ່າທຽມກັນ. "ຜົນກະທົບ Cantillon", ບ່ອນທີ່ຜູ້ທີ່ຢູ່ໃກ້ກັບແຫຼ່ງສ້າງເງິນໄດ້ຮັບຜົນປະໂຫຍດກ່ອນ. ນີ້ລວມເຖິງລັດຖະບານເອງ (ສະໜັບສະໜູນລາຍຈ່າຍ), ທະນາຄານໃຫຍ່ ແລະ Wall Street (ໄດ້ຮັບທຶນໃນອັດຕາດອກເບ້ຍຕ່ຳສຳລັບການກູ້ຢືມ ແລະ ການລົງທຶນ), ແລະ ບໍລິສັດໃຫຍ່ (ເຂົ້າເຖິງເງິນກູ້ທີ່ຖືກກວ່າສຳລັບການລົງທຶນ). ບຸກຄົນເຫຼົ່ານີ້ໄດ້ຊື້ຊັບສິນ ຫຼື ລົງທຶນກ່ອນທີ່ຜົນກະທົບຂອງເງິນເຟີ້ຈະເຮັດໃຫ້ລາຄາສູງຂຶ້ນ, ເຊິ່ງເຮັດໃຫ້ພວກເຂົາມີຂໍ້ໄດ້ປຽບ.
ຜົນກະທົບຕໍ່ຄົນທົ່ວໄປ
ສຳລັບຄົນທົ່ວໄປ, ຜົນກະທົບຂອງປະລິມານເງິນທີ່ເພີ່ມຂຶ້ນນີ້ແມ່ນການເພີ່ມຂຶ້ນຂອງລາຄາສິນຄ້າ ແລະ ການບໍລິການ - ນ້ຳມັນ, ຄ່າເຊົ່າ, ການດູແລສຸຂະພາບ, ອາຫານ, ແລະ ອື່ນໆ. ເນື່ອງຈາກຄ່າແຮງງານໂດຍທົ່ວໄປບໍ່ທັນກັບອັດຕາເງິນເຟີ້ນີ້, ອຳນາດການຊື້ຂອງປະຊາຊົນຈະຫຼຸດລົງເມື່ອເວລາຜ່ານໄປ. ມັນຄືກັບການແລ່ນໄວຂຶ້ນພຽງເພື່ອຢູ່ໃນບ່ອນເກົ່າ.
Bitcoin: ທາງເລືອກເງິນທີ່ໝັ້ນຄົງ
ຄວາມຂາດແຄນ: ບໍ່ຄືກັບເງິນຕາ fiat, Bitcoin ມີຂີດຈຳກັດສູງສຸດໃນປະລິມານຂອງມັນ. ຈະມີພຽງ 21 ລ້ານ Bitcoin ເທົ່ານັ້ນຖືກສ້າງຂຶ້ນ, ຂີດຈຳກັດນີ້ຝັງຢູ່ໃນໂຄດຂອງມັນ ແລະ ບໍ່ສາມາດປ່ຽນແປງໄດ້. ການສະໜອງທີ່ຈຳກັດນີ້ເຮັດໃຫ້ Bitcoin ເປັນເງິນຫຼຸດລາຄາ; ເມື່ອຄວາມຕ້ອງການເພີ່ມຂຶ້ນ, ມູນຄ່າຂອງມັນມີແນວໂນ້ມທີ່ຈະເພີ່ມຂຶ້ນເພາະວ່າປະລິມານການສະໜອງບໍ່ສາມາດຂະຫຍາຍຕົວ.
ຄວາມທົນທານ: Bitcoin ຢູ່ໃນ blockchain, ເຊິ່ງເປັນປຶ້ມບັນຊີສາທາລະນະທີ່ແບ່ງປັນກັນຂອງທຸກການເຮັດທຸລະກຳທີ່ແທບຈະເປັນໄປບໍ່ໄດ້ທີ່ຈະລຶບ ຫຼື ປ່ຽນແປງ. ປຶ້ມບັນຊີນີ້ຖືກກະຈາຍໄປທົ່ວພັນຄອມພິວເຕີ (nodes) ທົ່ວໂລກ. ແມ້ແຕ່ຖ້າອິນເຕີເນັດລົ້ມ, ເຄືອຂ່າຍສາມາດຢູ່ຕໍ່ໄປໄດ້ຜ່ານວິທີການອື່ນເຊັ່ນ: ດາວທຽມ ຫຼື ຄື້ນວິທະຍຸ. ມັນບໍ່ໄດ້ຮັບຜົນກະທົບຈາກການທຳລາຍທາງກາຍະພາບຂອງເງິນສົດ ຫຼື ການແຮັກຖານຂໍ້ມູນແບບລວມສູນ.
ການພົກພາ: Bitcoin ສາມາດຖືກສົ່ງໄປໃນທຸກບ່ອນໃນໂລກໄດ້ທັນທີ, 24/7, ດ້ວຍການເຊື່ອມຕໍ່ອິນເຕີເນັດ, ໂດຍບໍ່ຈຳເປັນຕ້ອງມີທະນາຄານ ຫຼື ການອະນຸຍາດຈາກພາກສ່ວນທີສາມ. ທ່ານສາມາດເກັບຮັກສາ Bitcoin ຂອງທ່ານໄດ້ດ້ວຍຕົນເອງໃນອຸປະກອນທີ່ເອີ້ນວ່າກະເປົາເຢັນ, ແລະ ຕາບໃດທີ່ທ່ານຮູ້ວະລີກະແຈລັບຂອງທ່ານ, ທ່ານສາມາດເຂົ້າເຖິງເງິນຂອງທ່ານຈາກກະເປົາທີ່ເຂົ້າກັນໄດ້, ເຖິງແມ່ນວ່າອຸປະກອນຈະສູນຫາຍ. ສິ່ງນີ້ສະດວກສະບາຍກວ່າ ແລະ ມີຄວາມສ່ຽງໜ້ອຍກວ່າການພົກພາເງິນສົດຈຳນວນຫຼາຍ ຫຼື ການນຳທາງການໂອນເງິນສາກົນທີ່ຊັບຊ້ອນ.
ການແບ່ງຍ່ອຍ: Bitcoin ສາມາດແບ່ງຍ່ອຍໄດ້ສູງ. ໜຶ່ງ Bitcoin ສາມາດແບ່ງເປັນ 100 ລ້ານໜ່ວຍຍ່ອຍທີ່ເອີ້ນວ່າ Satoshis, ເຊິ່ງອະນຸຍາດໃຫ້ສົ່ງ ຫຼື ຮັບຈຳນວນນ້ອຍໄດ້.
ຄວາມສາມາດໃນການທົດແທນກັນ: ໜຶ່ງ Bitcoin ທຽບເທົ່າກັບໜຶ່ງ Bitcoin ໃນມູນຄ່າ, ໂດຍທົ່ວໄປ. ໃນຂະນະທີ່ເງິນໂດລາແບບດັ້ງເດີມອາດສາມາດຖືກຕິດຕາມ, ແຊ່ແຂງ, ຫຼື ຍຶດໄດ້, ໂດຍສະເພາະໃນຮູບແບບດິຈິຕອນ ຫຼື ຖ້າຖືກພິຈາລະນາວ່າໜ້າສົງໄສ, ແຕ່ລະໜ່ວຍຂອງ Bitcoin ໂດຍທົ່ວໄປຖືກປະຕິບັດຢ່າງເທົ່າທຽມກັນ.
ການພິສູດຢັ້ງຢືນ: ທຸກການເຮັດທຸລະກຳ Bitcoin ຖືກບັນທຶກໄວ້ໃນ blockchain, ເຊິ່ງທຸກຄົນສາມາດເບິ່ງ ແລະ ພິສູດຢັ້ງຢືນ. ຂະບວນການພິສູດຢັ້ງຢືນທີ່ກະຈາຍນີ້, ດຳເນີນໂດຍເຄືອຂ່າຍ, ໝາຍຄວາມວ່າທ່ານບໍ່ຈຳເປັນຕ້ອງເຊື່ອຖືທະນາຄານ ຫຼື ສະຖາບັນໃດໜຶ່ງແບບມືດບອດເພື່ອຢືນຢັນຄວາມຖືກຕ້ອງຂອງເງິນຂອງທ່ານ.
ການຕ້ານການກວດກາ: ເນື່ອງຈາກບໍ່ມີລັດຖະບານ, ບໍລິສັດ, ຫຼື ບຸກຄົນໃດຄວບຄຸມເຄືອຂ່າຍ Bitcoin, ບໍ່ມີໃຜສາມາດຂັດຂວາງທ່ານຈາກການສົ່ງ ຫຼື ຮັບ Bitcoin, ແຊ່ແຂງເງິນຂອງທ່ານ, ຫຼື ຍຶດມັນ. ມັນເປັນລະບົບທີ່ບໍ່ຕ້ອງຂໍອະນຸຍາດ, ເຊິ່ງໃຫ້ຜູ້ໃຊ້ຄວບຄຸມເຕັມທີ່ຕໍ່ເງິນຂອງເຂົາເຈົ້າ.
ການກະຈາຍອຳນາດ: Bitcoin ຖືກຮັກສາໂດຍເຄືອຂ່າຍກະຈາຍຂອງບັນດາຜູ້ຂຸດທີ່ໃຊ້ພະລັງງານການຄິດໄລ່ເພື່ອຢັ້ງຢືນການເຮັດທຸລະກຳຜ່ານ "proof of work". ລະບົບທີ່ກະຈາຍນີ້ຮັບປະກັນວ່າບໍ່ມີຈຸດໃດຈຸດໜຶ່ງທີ່ຈະລົ້ມເຫຼວ ຫຼື ຄວບຄຸມ. ທ່ານບໍ່ໄດ້ເພິ່ງພາຂະບວນການທີ່ບໍ່ໂປ່ງໃສຂອງທະນາຄານກາງ; ລະບົບທັງໝົດໂປ່ງໃສຢູ່ໃນ blockchain. ສິ່ງນີ້ເຮັດໃຫ້ບຸກຄົນມີອຳນາດທີ່ຈະເປັນທະນາຄານຂອງຕົນເອງແທ້ ແລະ ຮັບຜິດຊອບຕໍ່ການເງິນຂອງເຂົາເຈົ້າ.
-
 @ 73cee26b:072f3bb6
2024-02-28 21:09:52
@ 73cee26b:072f3bb6
2024-02-28 21:09:52I haven't really been on nostr in a year or so, but playing around now it seems like there are WAY fewer zaps. There are some high-profile mega-zapped posts, but almost all posts and conversations are bereft of zaps. What happened? Recession?
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 3bf0c63f:aefa459d
2024-03-19 14:01:01
@ 3bf0c63f:aefa459d
2024-03-19 14:01:01Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Não tem solução
O melhor presidente dos últimos 50 anos, o melhor congresso, o melhor governador, os melhores ministros, um resultado eleitoral muito melhor do que o melhor dos meus sonhos e nada acontece.
A única solução que nos resta é o Bitcoin. Vale talvez a pena dar a vida pra tentar popularizar esse negócio.
-
 @ 65038d69:1fff8852
2025-03-31 12:13:39
@ 65038d69:1fff8852
2025-03-31 12:13:39Artificial intelligence is upon us and not showing any signs of slowing. The most common concern from those in the workforce is being replaced by one of these “thinking machines”. But what if AI wasn’t coming for your job? What if it was coming for your boss’s job instead?
I happened across the following post on X: https://x.com/BrianRoemmele/status/1905754986795151629 Brian describes having installed an AI system that provides an omniscient “shadow” to each of the executives at a client company, which can then be queried by the CEO for reports. The CEO seems to like it so far, and if it leads to less time spent writing internal reports I’m sure the executives like it too. But many of you may be recoiling at the thought of an always-on nanycam who’s sole purpose seems to be to snitch on you to your boss, and judging by the replies to Brian’s post, you’re not alone. If your supervisor has a history of targeting you your fears may not be misplaced. Workplace surveillance tools are often coyly marketed for this.
What if instead of your boss using an AI tool to spy on you, your boss was completely replaced by an AI? Would your supervisor having no biases or favouritism sway your opinion? What about being able to tailor its communication specifically to you? Expressing no judgement at your clarifying questions? Being immediately available 24/7? Perfectly equitable expectations and performance reviews? Just writing that almost has me convinced this would usher in a workplace utopia.
In practice guaranteeing zero bias is extremely difficult. After all, these things are programmed by humans and learn from human data. Their “weights” could also be intentionally adjusted to favour or target. If the AI’s supervisor follows the Pareto Principle (also known as the 80/20 Rule) they may be tempted to ask it for a list of the lowest performing employees to be laid off on a regular basis. Not keeping yourself in the top 20% of performers (by whatever metrics the AI has been programmed to look for) may mean your job. The dystopian-future videogame “Cyberpunk 2077” tells a story of a company that brings in an AI only to have it fire all the human workers in favour of automation and copies of itself. Clearly it’s implementers forgot to set hard limits on its executive powers. The shareholders were happy with all-time high profits though…
When technology is blamed for these sorts of existential problems the IT industry collectively sighs and repeats the mantra, “The problem is not the technology. The problem is the people.” A quote from a 1979 IBM presentation is likewise summoned; “A computer can never be held accountable, therefore a computer must never make a management decision.” As a darker example, the Nuremberg trials post-WWII saw the precedent set that acting under “superior orders” is not a valid defence for war crimes or crimes against humanity. It seems responsibility can’t be passed to others, whether man or machine. The endless task of generating reports and presentations can probably be automated away though.
Would you work under an AI, or “hire” an AI to manage others? We can help you with that; you can find us at scalebright.ca.
-
 @ 9e69e420:d12360c2
2025-01-26 01:31:31
@ 9e69e420:d12360c2
2025-01-26 01:31:31Chef's notes
arbitray
- test
- of
- chefs notes
hedding 2
Details
- ⏲️ Prep time: 20
- 🍳 Cook time: 1 hour
- 🍽️ Servings: 5
Ingredients
- Test ingredient
- 2nd test ingredient
Directions
- Bake
- Cool
-
 @ 000002de:c05780a7
2024-01-15 18:45:25
@ 000002de:c05780a7
2024-01-15 18:45:25Last night my lovely wife and I watched the film Kill the Messenger. It had been on my list for some time but we'd never gotten around to watching it.
From the book of knowledge
It is based on the book of the same name by Nick Schou and the book Dark Alliance by Gary Webb. The film stars Jeremy Renner, who also produced the film. The film was released on October 10, 2014, and depicts a reporter's suppressed attempts to cover the CIA involvement and secret support of large scale cocaine sales to fund the Nicaraguan Contras.
I have been familiar with the story but never read either of the books. What hit me after watching the movie was the fact that despite the many times that the absolute evil of the state is exposed, we do not see significant change. It is pretty depressing to come to the conclusion that even when the US government's lies and evil is exposed it continues to go on largely unabated. As far as I know little of consequence happened due to Gary Webb's brave work.
It reminded me of Edward Snowden's revelations. I believe they have had a larger impact but still not nearly the impact I had hoped for. In the film they do a good job of showing some of the many tactics used when someone starts exposing the state for what it is. First they change the focus of the allegations making them harder to believe or harder to prove. They overstate the case. In Webb's case the media pushed a narrative (pushed by the CIA) that Webb was saying the CIA targeted the black community with crack cocaine. Actually Webb discovered that the CIA used drugs to fund their operations. He didn't claim the CIA was directly selling drugs to blacks. See the difference. What happened was a consequence of the CIA's action but unlikely the goal. But this framing makes Webb sound more extreme.
This happened with Snowden and also during the Covid19 pandemic. Its a tactic that works on the masses. Make your opponents sound unreasonable. Make them toxic. The second tactic they point out is attacking the messenger. They go after the person and find flaws. Highlight them and do character assassination. Never mind that most of the "leaders" in most democracies are full of similar character flaws and mistakes. That is never brought up in this context.
The third tactic that jumped out at me was the divide and conquer strategy. The CIA actions that are the subject of this film happened under Reagan, a Republican. So of course his opponents show much interest and John Kerry investigated it. The common thread I see here is that these types of things are bi-partisan. If you don't believe me you aren't paying attention or you have been indoctrinated into the matrix. The CIA is a permanent fixture in US government like many tentacles of the state yet when something like this is exposed it quickly becomes consumed by party politics. I get it. I don't think it is a conspiracy, it is simple game theory. Politicians simply want power and will use anything to win over their opponents. The result however is that the real root issues are never solved. The CIA is not reformed or dismantled. Real change doesn't happen because real consequences never occur. I don't think the filmmakers intend to make this point but it struck me. If you study the history of the CIA you will see that they have a long track record of this type of behavior. If it is a strategy, its genius. Get the public focused on party politics on the puppets, not the real power centers.
The final tactic that saw expressed was on the black community. It is possible that the CIA intentionally wanted to push crack into these communities. I just haven't seen that demonstrated. In truth, it doesn't matter. The real issue is that the CIA didn't care. The ends justify the means. The consequences of the CIA's actions led to massive death and destruction in places like Los Angeles. It makes me sick as I write this. For what? To fund fighters in a foreign conflict? Please. In the film they show various "leaders" in the black community from that time. It seems obvious to me that these people while they are speaking many truths seem to be doing so for their own profit just as the politicians do. Some of them were politicians. Did they actually put their necks on the line and keep pushing for change? I would argue no. They focused on the CIA's tactic. They sold the distortion that Webb was clamming the CIA targeted their communities.
Now, this all left me feeling depressed. Many believe that if we could just expose the evils of the world that would be enough. It isn't sadly. The masses do not have the attention span nor the desire to question their programming. That's my experience at least having talked with many friends and family over the years. I've been aware and a follower of politics since my early years as a pre-teen. I was and still am a nerd. I have a fairly long memory and it still to this day blows my mind how little people seem to notice. How they seem to not notice that politicians always promise things they can't or won't deliver. Yet they still seem to believe in democracy and their team. They are blind to the manipulation. To the repeated failures. To the repeated exposures of the truth.
So, I am sitting there feeling down about all this. Talking to my wife about it and then I remembered bitcoin exists. And I told her, this is one reason why bitcoin is hopeful for me. The state has much of its power due to its ability to print money. Taking that power from them alone will not affect the change we want but it is a huge start. It would limit the ability to wage these wars that kill so many people. It would limit their reckless spending and force them to steal in more obvious ways. Ways that will piss more people off. So bitcoin is hopeful.
What do you think? I was a teen when these events happened. I'm curious what I've missed and maybe if I got some things wrong. I remember this story being published and I also remember Webb's death which is a whole other story.
-
 @ 3bf0c63f:aefa459d
2020-09-07 19:10:00
@ 3bf0c63f:aefa459d
2020-09-07 19:10:00O VAR é o grande equalizador
Não tenho acompanhado o futebol desde 2013 ou 2014, mas me parece que, como poderia ter sido previsto, o VAR tem favorecido os times pequenos ou marginais em detrimento dos demais.
É lógico: se os juízes favoreriam mais o Flamengo e o Corinthians, e depois os grandes de Rio e São Paulo, em detrimento dos demais, o VAR, por minimamente mais justo que seja, aparentará favorecer os outros.
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:12:19
@ 4ba8e86d:89d32de4
2025-04-21 02:12:19SISTEMA OPERACIONAL MÓVEIS
GrapheneOS : https://njump.me/nevent1qqs8t76evdgrg4qegdtyrq2rved63pr29wlqyj627n9tj4vlu66tqpqpzdmhxue69uhk7enxvd5xz6tw9ec82c30qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqppcqec9
CalyxOS : https://njump.me/nevent1qqsrm0lws2atln2kt3cqjacathnw0uj0jsxwklt37p7t380hl8mmstcpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3vamnwvaz7tmwdaehgu3wvf3kstnwd9hx5cf0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgcwaehxw309aex2mrp0yhxxatjwfjkuapwveukjtcpzpmhxue69uhkummnw3ezumt0d5hszrnhwden5te0dehhxtnvdakz7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309ahx7um5wghxymmwva3x7mn89e3k7mf0qythwumn8ghj7cn5vvhxkmr9dejxz7n49e3k7mf0qyg8wumn8ghj7mn09eehgu3wvdez7smttdu
LineageOS : https://njump.me/nevent1qqsgw7sr36gaty48cf4snw0ezg5mg4atzhqayuge752esd469p26qfgpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpnvm779
SISTEMA OPERACIONAL DESKTOP
Tails : https://njump.me/nevent1qqsf09ztvuu60g6xprazv2vxqqy5qlxjs4dkc9d36ta48q75cs9le4qpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz34ag5t
Qubes OS : https://njump.me/nevent1qqsp6jujgwl68uvurw0cw3hfhr40xq20sj7rl3z4yzwnhp9sdpa7augpzpmhxue69uhkummnw3ezumt0d5hsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshsz9thwden5te0dehhxarj9ehhsarj9ejx2a30qyg8wumn8ghj7mn09eehgu3wvdez7qg4waehxw309aex2mrp0yhxgctdw4eju6t09uqjxamnwvaz7tmwdaehgu3dwejhy6txd9jkgtnhv4kxcmmjv3jhytnwv46z7qgwwaehxw309ahx7uewd3hkctcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uj3ljr8
Kali linux : https://njump.me/nevent1qqswlav72xdvamuyp9xc38c6t7070l3n2uxu67ssmal2g7gv35nmvhspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswt9rxe
Whonix : https://njump.me/nevent1qqs85gvejvzhk086lwh6edma7fv07p5c3wnwnxnzthwwntg2x6773egpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3wamnwvaz7tmzw33ju6mvv4hxgct6w5hxxmmd9uq3qamnwvaz7tmwduh8xarj9e3hytcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz7qg7waehxw309ahx7um5wgkkgetk9emk2mrvdaexgetj9ehx2ap0sen9p6
Kodachi : https://njump.me/nevent1qqsf5zszgurpd0vwdznzk98hck294zygw0s8dah6fpd309ecpreqtrgpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszgmhwden5te0dehhxarj94mx2unfve5k2epwwajkcmr0wfjx2u3wdejhgtcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzpmhxue69uhkumewwd68ytnrwghszfrhwden5te0dehhxarj9eex7atwv3ex7cmtvf5hgcm0d9hx2unn9e3k7mf0qyvhwumn8ghj7mn0wd68ytnzdahxwcn0denjucm0d5hszrnhwden5te0dehhxtnvdakz7qgkwaehxw309ahx7um5wghxycmg9ehxjmn2vyhsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshs94a4d5
PGP
Openkeychain : https://njump.me/nevent1qqs9qtjgsulp76t7jkquf8nk8txs2ftsr0qke6mjmsc2svtwfvswzyqpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs36mp0w
Kleopatra : https://njump.me/nevent1qqspnevn932hdggvp4zam6mfyce0hmnxsp9wp8htpumq9vm3anq6etsppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpuaeghp
Pgp : https://njump.me/nevent1qqsggek707qf3rzttextmgqhym6d4g479jdnlnj78j96y0ut0x9nemcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgptemhe
Como funciona o PGP? : https://njump.me/nevent1qqsz9r7azc8pkvfmkg2hv0nufaexjtnvga0yl85x9hu7ptpg20gxxpspremhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet59upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy259fhs
Por que eu escrevi PGP. - Philip Zimmermann.
https://njump.me/nevent1qqsvysn94gm8prxn3jw04r0xwc6sngkskg756z48jsyrmqssvxtm7ncpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtchzxnad
VPN
Vpn : https://njump.me/nevent1qqs27ltgsr6mh4ffpseexz6s37355df3zsur709d0s89u2nugpcygsspzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqshzu2fk
InviZible Pro : https://njump.me/nevent1qqsvyevf2vld23a3xrpvarc72ndpcmfvc3lc45jej0j5kcsg36jq53cpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy33y5l4
Orbot: https://njump.me/nevent1qqsxswkyt6pe34egxp9w70cy83h40ururj6m9sxjdmfass4cjm4495stft593
I2P
i2p : https://njump.me/nevent1qqsvnj8n983r4knwjmnkfyum242q4c0cnd338l4z8p0m6xsmx89mxkslx0pgg
Entendendo e usando a rede I2P : https://njump.me/nevent1qqsxchp5ycpatjf5s4ag25jkawmw6kkf64vl43vnprxdcwrpnms9qkcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpvht4mn
Criando e acessando sua conta Email na I2P : https://njump.me/nevent1qqs9v9dz897kh8e5lfar0dl7ljltf2fpdathsn3dkdsq7wg4ksr8xfgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpw8mzum
APLICATIVO 2FA
Aegis Authenticator : https://njump.me/nevent1qqsfttdwcn9equlrmtf9n6wee7lqntppzm03pzdcj4cdnxel3pz44zspz4mhxue69uhhyetvv9ujumn0wd68ytnzvuhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqscvtydq
YubiKey : https://njump.me/nevent1qqstsnn69y4sf4330n7039zxm7wza3ch7sn6plhzmd57w6j9jssavtspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzueyvgt
GERENCIADOR DE SENHAS
KeepassDX: https://njump.me/nevent1qqswc850dr4ujvxnmpx75jauflf4arc93pqsty5pv8hxdm7lcw8ee8qpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpe0492n
Birwaden: https://njump.me/nevent1qqs0j5x9guk2v6xumhwqmftmcz736m9nm9wzacqwjarxmh8k4xdyzwgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpwfe2kc
KeePassXC: https://njump.me/nevent1qqsgftcrd8eau7tzr2p9lecuaf7z8mx5jl9w2k66ae3lzkw5wqcy5pcl2achp
CHAT MENSAGEM
SimpleXchat : https://njump.me/nevent1qqsds5xselnnu0dyy0j49peuun72snxcgn3u55d2320n37rja9gk8lgzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgmcmj7c
Briar : https://njump.me/nevent1qqs8rrtgvjr499hreugetrl7adkhsj2zextyfsukq5aa7wxthrgcqcg05n434
Element Messenger : https://njump.me/nevent1qqsq05snlqtxm5cpzkshlf8n5d5rj9383vjytkvqp5gta37hpuwt4mqyccee6
Pidgin : https://njump.me/nevent1qqsz7kngycyx7meckx53xk8ahk98jkh400usrvykh480xa4ct9zlx2c2ywvx3
E-MAIL
Thunderbird: https://njump.me/nevent1qqspq64gg0nw7t60zsvea5eykgrm43paz845e4jn74muw5qzdvve7uqrkwtjh
ProtonMail : https://njump.me/nevent1qqs908glhk68e7ms8zqtlsqd00wu3prnpt08dwre26hd6e5fhqdw99cppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpeyhg4z
Tutonota : https://njump.me/nevent1qqswtzh9zjxfey644qy4jsdh9465qcqd2wefx0jxa54gdckxjvkrrmqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5hzhkv
k-9 mail : https://njump.me/nevent1qqs200g5a603y7utjgjk320r3srurrc4r66nv93mcg0x9umrw52ku5gpr3mhxue69uhkummnw3ezuumhd9ehxtt9de5kwmtp9e3kstczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgacflak
E-MAIL-ALIÁS
Simplelogin : https://njump.me/nevent1qqsvhz5pxqpqzr2ptanqyqgsjr50v7u9lc083fvdnglhrv36rnceppcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp9gsr7m
AnonAddy : https://njump.me/nevent1qqs9mcth70mkq2z25ws634qfn7vx2mlva3tkllayxergw0s7p8d3ggcpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs6mawe3
NAVEGADOR
Navegador Tor : https://njump.me/nevent1qqs06qfxy7wzqmk76l5d8vwyg6mvcye864xla5up52fy5sptcdy39lspzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdp0urw
Mullvap Browser : https://njump.me/nevent1qqs2vsgc3wk09wdspv2mezltgg7nfdg97g0a0m5cmvkvr4nrfxluzfcpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpj8h6fe
LibreWolf : https://njump.me/nevent1qqswv05mlmkcuvwhe8x3u5f0kgwzug7n2ltm68fr3j06xy9qalxwq2cpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuv2hxr
Cromite : https://njump.me/nevent1qqs2ut83arlu735xp8jf87w5m3vykl4lv5nwkhldkqwu3l86khzzy4cpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs3dplt7
BUSCADORES
Searx : https://njump.me/nevent1qqsxyzpvgzx00n50nrlgctmy497vkm2cm8dd5pdp7fmw6uh8xnxdmaspr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp23z7ax
APP-STORE
Obtainium : https://njump.me/nevent1qqstd8kzc5w3t2v6dgf36z0qrruufzfgnc53rj88zcjgsagj5c5k4rgpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyarmca3
F-Droid : https://njump.me/nevent1qqst4kry49cc9g3g8s5gdnpgyk3gjte079jdnv43f0x4e85cjkxzjesymzuu4
Droid-ify : https://njump.me/nevent1qqsrr8yu9luq0gud902erdh8gw2lfunpe93uc2u6g8rh9ep7wt3v4sgpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsfzu9vk
Aurora Store : https://njump.me/nevent1qqsy69kcaf0zkcg0qnu90mtk46ly3p2jplgpzgk62wzspjqjft4fpjgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzrpmsjy
RSS
Feeder : https://njump.me/nevent1qqsy29aeggpkmrc7t3c7y7ldgda7pszl7c8hh9zux80gjzrfvlhfhwqpp4mhxue69uhkummn9ekx7mqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgsvzzjy
VIDEOO CONFERENCIA
Jitsi meet : https://njump.me/nevent1qqswphw67hr6qmt2fpugcj77jrk7qkfdrszum7vw7n2cu6cx4r6sh4cgkderr
TECLADOS
HeliBoard : https://njump.me/nevent1qqsyqpc4d28rje03dcvshv4xserftahhpeylu2ez2jutdxwds4e8syspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsr8mel5
OpenBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
FlorisBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
MAPAS
Osmand : https://njump.me/nevent1qqsxryp2ywj64az7n5p6jq5tn3tx5jv05te48dtmmt3lf94ydtgy4fgpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs54nwpj
Organic maps : https://njump.me/nevent1qqstrecuuzkw0dyusxdq7cuwju0ftskl7anx978s5dyn4pnldrkckzqpr4mhxue69uhkummnw3ezumtp0p5k6ctrd96xzer9dshx7un8qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpl8z3kk
TRADUÇÃO
LibreTranslate : https://njump.me/nevent1qqs953g3rhf0m8jh59204uskzz56em9xdrjkelv4wnkr07huk20442cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzeqsx40
REMOÇÃO DOS METADADOS
Scrambled Exif : https://njump.me/nevent1qqs2658t702xv66p000y4mlhnvadmdxwzzfzcjkjf7kedrclr3ej7aspyfmhxue69uhk6atvw35hqmr90pjhytngw4eh5mmwv4nhjtnhdaexcep0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpguu0wh
ESTEGANOGRAFIA
PixelKnot: https://njump.me/nevent1qqsrh0yh9mg0lx86t5wcmhh97wm6n4v0radh6sd0554ugn354wqdj8gpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyuvfqdp
PERFIL DE TRABALHO
Shelter : https://njump.me/nevent1qqspv9xxkmfp40cxgjuyfsyczndzmpnl83e7gugm7480mp9zhv50wkqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdnu59c
PDF
MuPDF : https://njump.me/nevent1qqspn5lhe0dteys6npsrntmv2g470st8kh8p7hxxgmymqa95ejvxvfcpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs4hvhvj
Librera Reader : https://njump.me/nevent1qqsg60flpuf00sash48fexvwxkly2j5z9wjvjrzt883t3eqng293f3cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz39tt3n
QR-Code
Binary Eye : https://njump.me/nevent1qqsz4n0uxxx3q5m0r42n9key3hchtwyp73hgh8l958rtmae5u2khgpgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdmn4wp
Climático
Breezy Weather : https://njump.me/nevent1qqs9hjz5cz0y4am3kj33xn536uq85ydva775eqrml52mtnnpe898rzspzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgpd3tu8
ENCRYPTS
Cryptomator : https://njump.me/nevent1qqsvchvnw779m20583llgg5nlu6ph5psewetlczfac5vgw83ydmfndspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsx7ppw9
VeraCrypt : https://njump.me/nevent1qqsf6wzedsnrgq6hjk5c4jj66dxnplqwc4ygr46l8z3gfh38q2fdlwgm65ej3
EXTENSÕES
uBlock Origin : https://njump.me/nevent1qqswaa666lcj2c4nhnea8u4agjtu4l8q89xjln0yrngj7ssh72ntwzql8ssdj
Snowflake : https://njump.me/nevent1qqs0ws74zlt8uced3p2vee9td8x7vln2mkacp8szdufvs2ed94ctnwchce008
CLOUD
Nextcloud : https://njump.me/nevent1qqs2utg5z9htegdtrnllreuhypkk2026x8a0xdsmfczg9wdl8rgrcgg9nhgnm
NOTEPAD
Joplin : https://njump.me/nevent1qqsz2a0laecpelsznser3xd0jfa6ch2vpxtkx6vm6qg24e78xttpk0cpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpdu0hft
Standard Notes : https://njump.me/nevent1qqsv3596kz3qung5v23cjc4cpq7rqxg08y36rmzgcrvw5whtme83y3s7tng6r
MÚSICA
RiMusic : https://njump.me/nevent1qqsv3genqav2tfjllp86ust4umxm8tr2wd9kq8x7vrjq6ssp363mn0gpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqg42353n
ViMusic : https://njump.me/nevent1qqswx78559l4jsxsrygd8kj32sch4qu57stxq0z6twwl450vp39pdqqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzjg863j
PODCAST
AntennaPod : https://njump.me/nevent1qqsp4nh7k4a6zymfwqqdlxuz8ua6kdhvgeeh3uxf2c9rtp9u3e9ku8qnr8lmy
VISUALIZAR VIDEO
VLC : https://njump.me/nevent1qqs0lz56wtlr2eye4ajs2gzn2r0dscw4y66wezhx0mue6dffth8zugcl9laky
YOUTUBE
NewPipe : https://njump.me/nevent1qqsdg06qpcjdnlvgm4xzqdap0dgjrkjewhmh4j3v4mxdl4rjh8768mgdw9uln
FreeTube : https://njump.me/nevent1qqsz6y6z7ze5gs56s8seaws8v6m6j2zu0pxa955dhq3ythmexak38mcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5lkjvv
LibreTube : https://snort.social/e/nevent1qqstmd5m6wrdvn4gxf8xyhrwnlyaxmr89c9kjddvnvux6603f84t3fqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsswwznc
COMPARTILHAMENTO DE ARQUIVOS
OnionShare : https://njump.me/nevent1qqsr0a4ml5nu6ud5k9yzyawcd9arznnwkrc27dzzc95q6r50xmdff6qpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qgswaehxw309ahx7tnnw3ezucmj9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qgswaehxw309ahx7um5wghx6mmd9uqjgamnwvaz7tmwdaehgu3wwfhh2mnywfhkx6mzd96xxmmfdejhyuewvdhk6tcppemhxue69uhkummn9ekx7mp0qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qyv8wumn8ghj7un9d3shjtnrw4e8yetwwshxv7tf9ut7qurt
Localsend : https://njump.me/nevent1qqsp8ldjhrxm09cvvcak20hrc0g8qju9f67pw7rxr2y3euyggw9284gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuyghqr
Wallet Bitcoin
Ashigaru Wallet : https://njump.me/nevent1qqstx9fz8kf24wgl26un8usxwsqjvuec9f8q392llmga75tw0kfarfcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgvfsrqp
Samourai Wallet : https://njump.me/nevent1qqstcvjmz39rmrnrv7t5cl6p3x7pzj6jsspyh4s4vcwd2lugmre04ecpr9mhxue69uhkummnw3ezucn0denkymmwvuhxxmmd9upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy3rg4qs
CÂMERA
opencamera : https://njump.me/nevent1qqs25glp6dh0crrjutxrgdjlnx9gtqpjtrkg29hlf7382aeyjd77jlqpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqssxcvgc
OFFICE
Collabora Office : https://njump.me/nevent1qqs8yn4ys6adpmeu3edmf580jhc3wluvlf823cc4ft4h0uqmfzdf99qpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsj40uss
TEXTOS
O manifesto de um Cypherpunk : https://njump.me/nevent1qqsd7hdlg6galn5mcuv3pm3ryfjxc4tkyph0cfqqe4du4dr4z8amqyspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzal0efa
Operations security ( OPSEC) : https://snort.social/e/nevent1qqsp323havh3y9nxzd4qmm60hw87tm9gjns0mtzg8y309uf9mv85cqcpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz8ej9l7
O MANIFESTO CRIPTOANARQUISTA Timothy C. May – 1992. : https://njump.me/nevent1qqspp480wtyx2zhtwpu5gptrl8duv9rvq3mug85mp4d54qzywk3zq9gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz5wq496
Declaração de independência do ciberespaço
- John Perry Barlow - 1996 : https://njump.me/nevent1qqs2njsy44n6p07mhgt2tnragvchasv386nf20ua5wklxqpttf6mzuqpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsukg4hr
The Cyphernomicon: Criptografia, Dinheiro Digital e o Futuro da Privacidade. escrito por Timothy C. May -Publicado em 1994. :
Livro completo em PDF no Github PrivacyOpenSource.
https://github.com/Alexemidio/PrivacyOpenSource/raw/main/Livros/THE%20CYPHERNOMICON%20.pdf Share
-
 @ 04222fa1:634e9de5
2024-03-07 10:02:06
@ 04222fa1:634e9de5
2024-03-07 10:02:06As the price of Bitcoin hits the headlines once again, the normies get interested
At my sauna last night we got on to the subject
I stayed pretty quiet, then one guy in the corner says...
It's the currency of the dark web, only criminals use it. OK pretty standard response
Next guy says...
You need two accounts, one for the hackers to find and a secret one
Then another interjected....
Do I go to the bank and ask them to put it in my account? Like, how do I buy it
And another....
You have to open your account abroad to be 100% safe
Safe to say we are early
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 3bf0c63f:aefa459d
2019-10-04 00:00:00
@ 3bf0c63f:aefa459d
2019-10-04 00:00:00mcldsp
A tool that migrates data from a c-lightning SQLite3 database into PostgreSQL so one can keep Lightning channels and everything but change the underlying database.
It's a mostly manual thing, and I keep following changes in the database schema on c-lightning's GitHub repo so I can update the migration specs whenever needed.
See also
-
 @ 3bf0c63f:aefa459d
2017-03-31 00:00:00
@ 3bf0c63f:aefa459d
2017-03-31 00:00:00Sistemas legais anárquicos
São poucos os exemplos de sistemas legais claramente anárquicos que nós temos, e são sempre de tempos muito remoto, da idade média ou por aí. Me vêm à cabeça agora o sistema islandês, o somaliano, o irlandês e as cortes dos mercadores da Europa continental.
Esses exemplos, embora sempre pareçam aos olhos de um libertário convicto a prova cabal de que a sociedade sem o Estado é capaz de fazer funcionar sistemas legais eficientes, complexos e muito melhores e mais baratos do que os estatais, a qualquer observador não entusiasmado vão parecer meio anacrônicos: são sempre coisas que envolvem família, clãs, chefes de família, comunidades pequenas -- fatores quase sempre ausentes na sociedade hoje --, o que dá espaço para que a pessoa pense (e eu confesso que isso também sempre me incomodou) que nada disso funcionaria hoje, são bonitos, mas sistemas que só funcionariam nos tempos de antigamente, o Estado com seu sistema judiciário é a evolução natural e necessária de tudo isso e assim por diante.
Vale lembrar, porém, que os exemplos que nós temos provavelmente não surgiram espontamente, eles mesmos foram o resultado de uma evolução lenta mas constante do sistema legal das suas respectivas comunidades. Se não tivessem sido interrompidos pela intervenção de algum Estado, esses sistemas teriam continuado evoluindo e hoje, quem sabe, seriam redes complexas altamente eficientes, que, por que não, juntariam tecnologias similares à internet com segurança de dados, algoritmos maravilhosos de reputação e voto, tudo decentralizado, feito por meio de protocolos concorrentes mas padronizados -- talvez, se tivessem tido um pouquinho mais de tempo, cada um desses sistemas legais anárquicos teria desenvolvido meios de evitar a conquista ou a concorrência desleal de um Estado, ou pelo menos do Estado como nós o conhecemos hoje.
-
 @ ff517fbf:fde1561b
2025-03-30 04:43:09
@ ff517fbf:fde1561b
2025-03-30 04:43:09ビットコインが「最強の担保」と言われる理由
ビットコインは「デジタルゴールド」とも呼ばれることがありますが、実はローンの担保としても最強だと言われています。その理由を、他の資産(株式、不動産、金など)と比較しながら見てみましょう。
-
流動性と即時性:ビットコインは24時間365日世界中で取引されているため、非常に流動性が高い資産です。売買がすぐにできて価格も常に明確なので、担保評価がしやすく、お金を貸す側・借りる側双方に安心感を与えます。一方、株式や不動産は市場が営業時間内しか動かず、現金化にも時間がかかります。不動産は売却に数ヶ月かかることもありますし、金(ゴールド)は現物を保管・輸送する手間があります。ビットコインならネット上で即座に担保設定・解除ができるのです。
-
分割性と柔軟性:ビットコインは小数点以下8桁まで分割可能(1億分の1が最小単位の「サトシ」)なので、必要な額だけ正確に担保に充てることができます。他方、土地や建物を一部だけ担保に入れることは難しいですし、株式も1株未満の細かい調整はできません。ビットコインなら価値の微調整が容易で、担保として柔軟に扱えるのです。
-
管理のしやすさ(マルチシグによる信頼性):HodlHodlのLendでは、ビットコイン担保は2-of-3のマルチシグ契約で管理されます。これは「借り手・貸し手・プラットフォーム」の3者それぞれが鍵を持ち、2つの鍵の同意がないとビットコインを動かせない仕組みです。このため、誰か一人が勝手に担保を持ち逃げすることができず、第三者(HodlHodl)も単独ではコインを移動できません。ビットコインだからこそ実現できる非中央集権で安全な担保管理であり、株式や不動産を担保にする場合のように銀行や証券会社といった仲介業者に頼る必要がありません。
-
国境を越えた利用:ビットコインはインターネットがつながる所なら世界中どこでも送受信できます。このため、日本にいながら海外の相手とでもローン契約が可能です。たとえば日本の方がビットコインを担保にドル建てのステーブルコインを借り、それを日本円に換えて使うこともできます(為替リスクには注意ですが…)。不動産を海外の人と直接やり取りするのは現実的に難しいですが、ビットコインならグローバルに担保が活用できるのです。
-
希少性と価値の上昇期待:ビットコインは発行上限が決まっており(2100万BTCまで)、時間とともに新規供給が減っていきます。過去の長期的な価格推移を見ると、短期的な変動は激しいものの数年〜十年のスパンでは上昇傾向にあります。一方、法定通貨建ての資産(債券や株式など)はインフレの影響で実質価値が目減りすることがあります。ビットコインは長期保有すれば価値が上がりやすい特性があるため、「今手放したくない資産」として担保に向いています。実際、HodlHodlのチームは「ビットコインはスーパーカCollateral(超優秀な担保)だ」と述べています。
こうした理由から、ビットコインは現時点で考えうる中でも最良の担保資産と考えられています。株や不動産のように書類手続きや名義変更をしなくても、ビットコインならブロックチェーン上の契約でシンプルに担保設定ができる――この手軽さと信頼性が大きな魅力です。
匿名&プライバシー重視:KYC不要のP2Pレンディングのメリット
HodlHodlのLend最大の特徴の一つは、本人確認(KYC)が一切不要だという点です。日本の多くの金融サービスでは口座開設時に運転免許証やマイナンバー提出など煩雑な手続きが必要ですが、Lendではメールアドレスでアカウント登録するだけでOK。これは「匿名性・プライバシー」を重視する人にとって非常に相性が良いポイントです。
-
個人情報を晒さなくて良い安心感:日本では昔から「人に迷惑をかけない」「目立たない」ことが美徳とされ、特にお金の話は他人に知られたくないと考える人が多いですよね。Lendは匿名で利用できるため、借金をすることを周囲に知られたくない人でも安心です。銀行からローンを借りるときのように収入証明や保証人を用意する必要もなく、誰にも知られずひっそりと資金調達ができます。
-
ノー・チェック&ノー・ペーパー:貸し借りにあたって信用審査や過去の借入履歴チェックがありません 。極端な話、今まで金融履歴が全く無い人や、銀行に相手にされないような人でも、ビットコインさえ持っていればお金を借りられるのです。書類のやり取りが無いので手続きもスピーディーです。「印鑑証明や収入証明を揃えて…」という面倒とは無縁で、ネット上でクリックして契約が完結します。
-
プライバシーの保護:個人情報を提出しないということは、情報漏洩のリスクも無いということです。近年、日本でも個人情報の流出事件が相次いでおり、不安に感じる方も多いでしょう。Lendではアカウント登録時にメールアドレスとパスワード以外何も求められません。財務情報や身元情報がどこかに蓄積される心配がないのは、大きな安心材料です。
-
国や機関から干渉されにくい:匿名であるということは、極端に言えば誰にも利用を知られないということです。たとえば「ローンを借りると住宅ローンの審査に響くかな…」とか「副業の資金調達を会社に知られたくないな…」といった心配も、匿名のP2Pローンなら不要です。借りたお金の使い道も自由ですし、何より利用自体が自分だけの秘密にできるのは、日本人にとって心理的ハードルを下げてくれるでしょう。
このように、ノーKYC(本人確認なし) のP2Pレンディングは、日本のようにプライバシーや控えめさを重んじる文化圏でも利用しやすいサービスと言えます。実際、HodlHodlのLendは「地理的・規制的な制限がなく、世界中の誰もが利用できる純粋なP2P市場」とされています。日本に居ながらグローバルな貸し借りができ、しかも身元明かさずに済む――これは画期的ですね。
Borrow編:HodlHodlのLendでビットコインを担保にお金を借りる方法
それでは具体的に、HodlHodlのLendでどのようにビットコイン担保のローンを借りるのか、手順を追って説明します。初心者でも迷わないよう、シンプルなステップにまとめました。
1. アカウント登録 (Sign up)
まずはHodlHodlのLendサイトにアクセスし、無料のアカウントを作成します。必要なのはメールアドレスとパスワードだけです。登録後、確認メールが届くのでリンクをクリックして認証すれば準備完了。これでプラットフォーム上でオファー(契約希望)を閲覧・作成できるようになります。
※HodlHodlは日本語には対応していませんが、英語のシンプルなUIです。Google翻訳などを使っても良いでしょう。
2. 借りたい条件のオファーを探す or 作成
ログインしたら、「To Borrow(借りる)」のメニューから現在出ている貸し手のオファー一覧を見てみましょう。オファーには借入希望額(例:$1000相当のUSDT)、期間(例:3ヶ月)、金利(例:5%)やLTV(担保価値比率、例:60%)などの条件が書かれています。自分の希望に合うものがあれば選んで詳細画面へ進みます。条件に合うオファーが見つからない場合は、自分で「○○ USDTを△ヶ月、金利○%で借りたい」という借り手オファーを新規作成することも可能です。
用語補足:LTV(ローン・トゥ・バリュー)とはローン額に対する担保価値の割合です。たとえばLTV50%なら、借りたい額の2倍の価値のビットコインを担保に入れる必要があります。LTVは貸し手が設定しており、一般に30%〜70%程度の範囲でオファーが出ています。低いLTVほど借り手は多くのBTC担保が必要ですが、その分だけ貸し手にとって安全なローンとなります。
3. 契約成立とマルチシグ担保のデポジット
借り手・貸し手双方が条件に合意すると契約成立です。HodlHodlプラットフォーム上で自動的に専用のマルチシグ・エスクロー用ビットコインアドレス(担保保管先アドレス)が生成されます。次に、借り手であるあなたは自分のウォレットからビットコインをそのエスクローアドレスに送金します。
- 📌ポイント:マルチシグで安心 – 上述の通り、このエスクロー用アドレスのコインを動かすには3者中2者の署名が必要です。あなた(借り手)は常にそのうちの1つの鍵を保有しています。つまり、自分が承認しない限り担保BTCが勝手に引き出されることはないのでご安心ください。
ビットコインの入金がブロックチェーン上で所定の承認(通常数ブロック程度)を得ると、担保デポジット完了です。これで契約は有効化され、次のステップへ進みます。
4. 貸し手から資金(ステーブルコイン)を受け取る
担保のロックが確認できると、今度は貸し手がローン金額の送金を行います。Lendで借りられるのは主にステーブルコインです。ステーブルコインとは、米ドルなど法定通貨の価値に連動するよう設計された仮想通貨で、USDTやUSDC、DAIといった種類があります。借り手は契約時に受取用のステーブルコインアドレス(自分のウォレットアドレス)を指定しますので、貸し手はそのアドレス宛に契約どおりの額を送金します。例えばUSDTを借りる契約なら、貸し手からあなたのUSDTウォレットにUSDTが送られてきます。
これで晴れて、あなた(借り手)は希望のステーブルコインを手にすることができました! あなたのビットコインは担保としてロックされていますが、期限までに返済すれば取り戻せますので、しばしのお別れです。借りたステーブルコインは自由に使えますので、後述する活用例を参考に有効活用しましょう。
5. 返済(リペイメント)
契約期間中は基本的に何もする必要はありません(途中で追加担保や一部返済を行うことも可能ですが、初心者向け記事では割愛します)。期間が満了するまでに、借りたステーブルコイン+利息を貸し手に返済します。返済も、貸し手の指定するウォレットアドレスにステーブルコインを送金する形で行われます。
- 利息の計算:利息は契約時に決めた率で発生します。例えば年利10%で6ヶ月間$1000を借りたなら、利息は単純計算で$50(=$1000×10%×0.5年)です。契約によっては「期間全体で○%」と定める場合もありますが、プラットフォーム上で年率(APR)換算が表示されます。
期間内であれば任意のタイミングで早期返済することも可能です。返済期限より早く全額返せば、利息もその日数分だけで済みます(※ただし契約によります。事前に契約条件を確認してください)。HodlHodlでは分割返済にも対応しており、例えば月ごとに少しずつ返して最後に完済することもできます。
6. ビットコイン担保の解除(返却)
貸し手があなたからの返済受領を確認すると、プラットフォーム上で契約終了の手続きを行います。マルチシグの担保アドレスからあなたのビットコインを解放(返却)する署名を貸し手とプラットフォームが行い、あなたの元のウォレットにビットコインが送られます。こうして無事に担保のBTCが戻ってくれば、一連のローン取引は完了です🎉。
もし返済が滞った場合はどうなるのでしょうか?その場合、契約で定められた猶予期間やマージンコール(追加担保のお願い)を経た後、担保のビットコインが強制的に貸し手に渡されて契約終了(清算)となります。担保額が未返済額を上回っていれば、差額は借り手に返ってきます。つまり、返せなかったとしても借り手が担保以上の損をすることはありませんが、大切なビットコインを失ってしまう結果にはなるので注意しましょう。
Borrow(借りる)側のまとめ:ビットコインさえあれば、あとの手続きは非常に簡単です。借入までの流れをもう一度簡潔にまとめると:
- メールアドレスでLendに登録
- 借入オファーを探すor作成してマッチング
- マルチシグ契約が自動生成・BTC担保を自分で入金
- 貸し手からステーブルコインを受領
- 期限までにステーブルコイン+利息を返済
- ビットコイン担保が自分のウォレットに戻る
第三者の仲介なしに、ネット上でこれだけのことが完結するのは驚きですよね。HodlHodlは「あなたの条件、あなたの鍵、あなたのコイン」と銘打っており、自分の望む条件で・自分が鍵を管理し・自分の資産を動かせるプラットフォームであることを強調しています。
Lend編:HodlHodlのプラットフォームでお金を貸してみよう
次は逆に、自分が貸し手(Lender)となってステーブルコインを貸し出し、利息収入を得る方法です。銀行に預けても超低金利のこのご時世、手持ちの資金をうまく運用したい方にとってP2Pレンディングは魅力的な選択肢になりえます。HodlHodlのLendなら、これもまた簡単な手順で始められます。
基本的な流れは先ほどの「Borrow編」と鏡写しになっています。
1. アカウント登録
借り手と同様、まずはHodlHodlに登録します(すでに借り手として登録済みなら同じアカウントで貸し手にもなれます)。メールアドレスだけでOK、もちろん貸し手側もKYC不要です。
2. 貸出オファーの確認 or 作成
ログイン後、「To Lend(貸す)」メニューから現在の借り手募集一覧を見ます。各オファーには希望額・期間・支払い利率・LTVなど条件が表示されています。「この条件なら貸してもいいかな」という案件があれば選択しましょう。もし自分の希望する利回りや期間が合わない場合は、自分で貸し手オファーを作成することも可能です。「○○ USDTまで、最長△ヶ月、最低利息◻◻%で貸せます」といった条件を提示できます。プラットフォーム上ではユーザーがお互いに条件を提示しあってマッチングする仕組みなので、金利や期間もすべてユーザー自身が自由に設定できます。
3. マッチングと契約開始
あなたの提示した条件で借りたい人が現れたら契約成立です(逆に誰かの借入オファーに応じる形なら、その時点で成立)。システムがマルチシグの担保用BTCアドレスを生成し、借り手がそこへビットコインをデポジットします。借り手からのBTC入金が確認できるまで、貸し手であるあなたは資金を送る必要はありません。担保が確保されたのを見届けてから次に進みます。
4. 資金(ステーブルコイン)の送金
借り手の担保ロックが完了したら、契約で定めたステーブルコインを借り手へ送金します。送金先アドレスは契約詳細画面に表示されます(借り手が指定済み)。例えばUSDCを貸す契約なら、相手のUSDCアドレスに約束の額を送ります。ここで送金した金額がローンの principal(元本)となり、後ほど利息とともに返ってくるわけです。
無事に相手に届けば、あとは契約期間終了まで待つだけです。あなたは担保のBTCに対して鍵を1つ持っている状態なので、万一トラブルが起きた場合でも担保を引き出す権利を部分的に持っています(詳しくは次ステップ)。
5. 返済の受領
契約期間が終わると、借り手があなたにステーブルコインを返済してくるはずです。約束どおり元本+利息を受け取ったら、それを確認してプラットフォーム上で「返済完了」を操作します。すると担保のビットコインがマルチシグから解放され、借り手に返却されます。これで貸し手としてのあなたは利息分の収益を獲得できました。お疲れ様です!
もし借り手が返済しなかった場合どうなるでしょうか?その場合、所定の猶予期間やマージンコール通知の後、担保のビットコインがあなた(貸し手)に渡されることになります。具体的には、LTVが90%に達するか返済期日から24時間以上滞納が続くと強制清算となり、担保BTCからあなたの貸付相当額が充当されます。担保が十分であれば元本と利息はカバーされ、余剰があれば借り手に返還されます。つまり貸し手側はかなり手厚く保護されており、返済を受け取れない場合でも担保で穴埋めされる仕組みです。
6. 収益を管理・再投資
受け取ったステーブルコイン(元本+利息)は再度プラットフォームで貸し出しても良いですし、他の用途に使ってもOKです。年利に換算するとだいたい10%前後の利回りになる案件が多く見られます。条件次第では更に高い利率の契約も可能ですが、その分借り手が見つかりにくかったりリスク(担保不足のリスク)が高まる可能性もあります。ご自身のリスク許容度に合わせて運用しましょう。
Lend(貸す)側のまとめ:
- HodlHodlに登録(メールアドレスのみ)
- 貸出オファーを提示 or 借り手募集に応じる
- 契約成立後、借り手がBTC担保を入金
- 貸し手(自分)がステーブルコインを送金
- 期限まで待ち、借り手から元本+利息を受領
- 担保BTCを返却し、利息収入を得る
銀行預金では考えられないような利息収入を得られるのが魅力ですが、その裏でビットコイン価格変動リスクも担っています。大暴落が起きて担保評価額が急落すると、清算時に元本を割るリスクもゼロではありません(LTV設定とマージンコール制度で極力保護されまますが)。リスクとリターンを理解した上で、小額から試すことをおすすめします。
ステーブルコインの活用:お金持ちは借金で生活する?
ここまで、ビットコインを手放さずにステーブルコインを手に入れる方法を見てきました。それでは、借りたステーブルコインは具体的に何に使えるのでしょうか?いくつか例を挙げてみましょう。
-
日常の出費に充当:ビットコイン投資家の中には「生活費はすべて借りたお金で賄い、自分のBTCはガチホ(売らずに長期保有)する」という方針の人もいます。例えば毎月の家賃や食費をステーブルコインのローンで支払い(これについても今後詳しく解説していきます)、ビットコインは一切使わないというイメージです。こうすれば、手持ちのBTCを売らずに済むので将来の値上がり益を逃しません。また日本では仮想通貨を売却すると雑所得として高率の税金がかかりますが、ローンで得たお金は借入金なので課税対象になりません(※将来的な税務計算は自己責任で行ってください)。つまり、ビットコインを売却して現金化する代わりにローンを使うことで、節税と資産温存のメリットが得られる可能性があります。
-
投資・資産運用に回す:借りた資金をさらに別の投資に活用することもできます。例えば有望な株式や不動産に投資したり、あるいは他の仮想通貨を買うこともできます。極端な例では、ビットコインを担保にUSDTを借りて、そのUSDTでまた別の仮想通貨を買い、それを運用益で返済する…といった戦略も理論上は可能です。ただし、借りたお金での投機はハイリスクなので慎重に!手堅い使い道としては、事業資金に充てるのも良いでしょう。例えば小さなオンラインビジネスを始めるための元手にしたり、新しい資格取得のための学費にするなど、自分への投資に使えば将来的なリターンでローンを返しつつ利益を上げることが期待できます。
-
急な支払いへの備え:人生何があるか分かりません。医療費や冠婚葬祭など急に現金が必要になる場面もあります。そんなとき、ビットコインをすぐ売ってしまうのは惜しい…という場合にローンで一時的にしのぐことができます。後で落ち着いてから返済すれば、大事なBTCを手放さずにピンチを乗り切れます。言わばデジタル質屋のような感覚で、ビットコインを預けてお金を工面し、後で買い戻す(返済する)イメージですね。日本でも昔から「質屋」で着物や宝石を預けてお金を借りる文化がありましたが、HodlHodl Lendはビットコイン版の質屋とも言えるでしょう。
-
市場の機会を逃さない:仮想通貨市場は変動が激しく、「今これを買いたいのに現金が無い!」というチャンスもあるでしょう。例えば「ビットコインが急落したから買い増したいが、現金が足りない」という場合、手持ちBTCを担保にしてステーブルコインを借り、その急落で安く買い増しする、といった動きもできます。そして後日価格が戻したところで返済すれば、差益を得つつBTC保有枚数も増やせるかもしれません。このようにローンを戦略的に使えば、市場の好機を掴む資金余力を生み出すことができます。ただしハイリスクな手法でもあるため、上級者向けではあります。
ここで覚えておきたいのは、「お金持ちは借金との付き合い方が上手い」という点です。日本では借金にネガティブな印象を持つ人も多いですが、世界的な資産家や大企業はしばしばあえて借金をして手元資金を他に活用しています。アメリカのベストセラー『金持ち父さん貧乏父さん』で有名なロバート・キヨサキ氏も「富裕層は他人のお金(借金)を利用してさらに富を築く」と強調しています。例えば彼は借金で高級車を買い、不動産投資にも借入を活用したそう (金持ちは貧乏人より借金が多い | 「金持ち父さん 貧乏父さん」日本オフィシャルサイト)❤️。借金を味方につけて資産運用すれば、自分の持ち出し資金を抑えつつ豊かな生活を実現できる可能性があります。
もちろん無計画な借金は禁物ですが、ローンを上手に使うことは決して悪いことではなく、むしろ経済的戦略として有効なのです。ビットコイン担保ローンはその新しい選択肢として、「お金にお金に働いてもらう」感覚を身につけるきっかけになるかもしれません。
高い金利でもローンを利用するのはなぜ?その理由と戦略
Lendのプラットフォームで提示される金利は、年利換算で見ると10〜15%程度が一つの目安 です。中にはそれ以上の利率の契約もあります。日本の銀行ローン(金利数%以下)と比べるとかなり高利に思えますが、それでも多くの人がこのサービスを利用してローンを組んでいます。なぜ高い利息を支払ってまで借りる価値があるのでしょうか?最後に、その理由と利用者の戦略について考えてみましょう。
-
(1) ビットコインの期待リターンが高い:借り手にとって一番の動機は、「ビットコインは将来もっと値上がりするはずだから、多少利息を払っても売りたくない」というものです。例えば年利15%で$1000借りると一年後に$1150返す必要がありますが、もしビットコイン価格がその間に15%以上上昇すれば、利息分を差し引いても得をする計算になります。過去のビットコイン相場は年率ベースで大きく成長した年も多く、強気のホルダーほど利息より値上がり益を優先する傾向があります。「金利よりビットコインの価値上昇のほうが大きい」という自信が、高金利を払ってでも借りる動機になっているのです。
-
(2) 課税や手数料の回避:先ほど述べたように、日本ではビットコインを売却すると高額の税金が発生する可能性があります。仮に30%〜50%の税金がかかるのであれば、年利10%前後のローンで済ませたほうがトクだという判断も成り立ちます。また、取引所で売却するときのスプレッドや出金手数料なども考えると、売却コストを回避する手段としてローンを選ぶ人もいます。要するに「売るくらいなら借りた方がマシ」という考え方ですね。
-
(3) 自由と速さを優先:従来の金融機関からお金を借りるには時間がかかりますし、使途にも制限があることが多いです(事業資金なのか生活費なのか、といった審査があります)。それに対してHodlHodlのP2Pローンは使い道自由・即日資金調達が可能です。利息が高めでも「今すぐ○○がしたい」「明日までに現金が要る」といったニーズには代えられません。特に仮想通貨業界はスピード命ですから、チャンスを逃さないために高コストでも素早く借りるという選択が生まれます。
-
(4) 借金=時間を買うこと:あるユーザーの言葉を借りれば、「借金をすることは未来の時間を先取りすること」でもあります。例えば住宅ローンがあるからこそ若い世代でもマイホームに住めますし、事業ローンがあるからこそ企業は成長の機会を掴めます。ビットコイン担保ローンも同じで、「今はお金が無いけど将来増やすアテはある。だから今借りてしまおう」というケースもあるでしょう。将来の収入や資産増加を見込んで、時間を味方につけるためにあえて借金をするのです。日本語では「借金してでも◯◯する」という表現がありますが、前向きな借金は将来への投資とも言えるでしょう。
-
(5) 非中央集権への支持:もう一つ見逃せないのは、HodlHodlのようなプラットフォームを利用する理由に思想的な支持があります。つまり「銀行や政府に頼らないお金の流れを実現したい」「ビットコインのエコシステムを活性化させたい」というビットコイナーたちです。多少コストが高くても、理念に共感して使っているケースもあります。匿名で自由にお金を借りられる世界を体験することで、金融システムの新たな可能性を感じているのです。
以上のように、高い金利にも関わらずローンを利用するのは明確なメリットや戦略があるからなのです。もちろん全ての人に当てはまるわけではありません。ビットコイン価格が下落局面ではリスクも伴いますし、利息分だけ損になる場合もあります。しかし、それらを理解した上で「自分のお金を働かせる」「資産を手放さずレバレッジを利かせる」手段として活用している人々が増えてきています。
最後に、HodlHodlの公式ブログの一文をご紹介します。
“私たちはビットコインこそがスーパーカ collateral(超優秀な担保)であり、利回りを得るために使うのではなく、それを担保に資金を借りるために使われるべきだと考えています" (The lending is dead, long live the lending | by Hodl Hodl | Hodl Hodl | Medium)。
ビットコイン時代の新しいお金の借り方・貸し方であるP2Pローン。最初は難しく感じるかもしれませんが、仕組みを理解すればとてもシンプルで強力なツールです。日本ではまだ馴染みが薄いかもしれませんが、匿名性を好み、コツコツ資産を増やすのが得意な人にこそフィットするサービスかもしれません。ぜひ少額から試し、自分なりの活用法を見つけてみてください。きっと新たな発見があるはずです。
もしビットコイン担保のP2Pローンなどについてもっと深く知りたい、あるいは個別に相談してみたいと思えば、どうぞお気軽にご連絡ください。1対1のコンサルティングも承っています。
サービスには決まった料金はありませんが、ご相談を通じて「役に立った」と思い、お悩みや疑問を解決できたと感じていただけたら、「3つのT」でのご支援(Value for Value)をぜひご検討ください:
- 時間(Time):この記事をSNSなどでシェアしていただくこと。
- 才能(Talent):コメントや補足情報などを通じて知識を共有していただくこと。
- 宝(Treasure):世界で最も健全なお金、ビットコインの最小単位「sats」でのご支援。
もちろん、支援の有無にかかわらず、お力になれればとても嬉しいです。 では、また次回!
-
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 57d1a264:69f1fee1
2024-03-05 07:31:05
@ 57d1a264:69f1fee1
2024-03-05 07:31:05What's your favorite paraphernalia, and how has it improved your life? What it has helped you design or accomplish lately?
-
 @ 65038d69:1fff8852
2025-03-29 13:05:35
@ 65038d69:1fff8852
2025-03-29 13:05:35Welcome to part 4, the final entry in the What is Money series. We’re capping it off with “crypto” and CBDCs.
Let's start with crypto. Short for cryptocurrency, it’s a catch-all term for all of the non-fiat, blockchain-based, or non-government-operated new money systems that aren’t Bitcoin. Ethereum, Solana, and Dogecoin are some you may have heard of. There are actually thousands of cryptocurrencies in existence, but we’ll summarize some of the biggest ones by size and pop culture penetration. One thing they all have in common is that like fiat currencies, they have no supply limit and are therefore inflationary by nature.
Ethereum: Released in 2015 by Vitalik Buterin, Ethereum is less of a money system and more of a network built to run “decentralized applications” (DAPs) on. “Smart contracts” and “tokens” are the most common of these. If none of those terms mean anything to you, you’re not alone. What they’ve essentially done is recreate the unending complexity of high finance in a computer system and replaced the bankers and lawyers with programmers.
Solana: Solana is much smaller than Ethereum but serves a similar function of being a wild-west finance platform. I’m only mentioning it here as it's been in the media a lot with numerous security compromises, lawsuits, and general drama. Your nephew who trades in Robux probably knows someone who lost their allowance savings in the 2021 crash.
USDT/Tether: This is the largest in a family of cryptocurrencies called “stablecoins”. They’re meant to offer the features of crypto but with the “stability” of having their value tied to a fiat currency, in this case the US Dollar.
Monero: Monero was designed from the ground up to be as anonymous as possible. Unfortunately it’s lack of popularity means it’s not particularly useful for purchases.
Dogecoin: Released in 2013, Dogecoin was created as a joke to poke fun at Bitcoin and cryptocurrencies. As a joke it’s been wildly successful, but like most jokes there are many who decided to take it seriously over the years, which has driven its market cap to surpass that of Monera and most others. It’s currently in the top 10 by market cap, but you’ll struggle to find anyone who takes it as payment.
The concept of CBDCs (central bank digital currencies) has been making the rounds through media for some time. Some paint it as a boogeyman to be feared, while others see it as nothing more than an annoying waste of government resources. As you may recall from part 2 of this series, the Bank of Canada is not a retail bank with individuals for customers, instead acting as an administrative body and a bank for banks. CBDCs have the potential to change that. In a sentence, a Canadian CBDC would most likely be a system whereby individuals who struggle to get or maintain accounts at retail banks could be issued a Bank of Canada account. There may also be some integration with Payments Canada systems to make retail payments and transfers cheaper and more direct. Much of this is speculation though, as the BoC hasn’t announced any of this, only that research is ongoing. In any case it won’t be a replacement of the Canadian Dollar, just another system for moving Dollars around between ledgers and accounts.
I’d normally sign off with something like, “Want help with insert article topic here? You can find us at scalebright.ca”, but in the case of crypto I’m afraid we must decline. The other trait shared by all of these money systems beside inflation via no supply limit is that they’re all scams designed to steal from their customers. Bitcoin is the only digital non-fiat currency this doesn't apply to. So if you’d like help with Bitcoin, you can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-29 13:02:18
@ 65038d69:1fff8852
2025-03-29 13:02:18Millennials remember the era of Buzzfeed quizzes with fondness, and some may even describe it as identity or culture shaping. People have always loved these miniature personality tests, and while Buzzfeed may no longer be in its heyday, the popularity of these dinner-table icebreakers has transcended generational gaps. To the analytically-brained among us this sounds like a datapoint that could be used in the workplace. Or is it?
You’ve probably heard someone’s answer to one of these and thought, “Oh wow, that sounds mildly psychopathic, I’m sure glad I don’t work with them!” Interviewers will sometimes ask questions like “if you were an animal, what kind of animal would you be?” as a conversation starter, but unscored. Part of the reason for this is that laws around discrimination in hiring make filtering via psychological or personality tests a grey area. Any suggestion of discrimination opens employers to potential lawsuits and investigations. Even if the applicant answered unironically with “I would be a dragon because I love hoarding gold and burning down unsuspecting villages!”, you would need to prove that the question was asked in a controlled environment by a certified professional and that the question was directly relevant to the position being applied for.
Now that I’ve most likely talked you out of implementing these in your interview processes, here are a handful of tests that, in an HR and legal department approved manner, could be run during an interview. Failing that, they make for great casual icebreakers! Their sources range from actual psychological tests to dubious corners of the internet, and they’ve all been simplified down to their simplest forms, so I’ll again warn that you’ll want to do diligence before suggesting their use in your workplace.
The Marshmallow Test: The test subjects (usually children) are offered a marshmallow and told that if they leave it for a few minutes, they can have two. Adults who’ve developed impulse control will usually say the correct answer is obvious, yet we fail slightly more complex versions all the time. Remember that greasy fast-food you bought with money you could have saved for a nice dinner out?
Cognitive Reflection Test (CRT): “Some apples and some bananas cost $1.10. The apples cost $1 more than the bananas. How much did the apples cost?” If you suspect a trick, you’ll probably think about the question a bit further, but the intuitive part of our brains want us to think the apples were $1 and the bananas $0.10.
The Breakfast Question: “How would you feel if you hadn’t eaten breakfast?” This one has some deep internet lore behind it, but the idea is that you’re testing the subject’s capacity for hypothetical reasoning. Can they process “what-ifs”? It can also extend into testing for empathy (“How would you feel if you were in Steve’s shoes and someone stole your ice cream?”).
Thematic Apperception Test (TAT): Show the subject an ambiguous picture (ideally emotionally neutral) with people in it and ask them to imagine what is happening, including what the people are thinking and feeling. Most people will subconsciously project their own thoughts and feelings onto the characters in the picture.
Moral Circle Test: This one has a history of being misunderstood and used as a political cudgel, so you may want to save it for your more understanding friends. Subjects were asked to rank the moral responsibilities they felt toward increasingly distant groups, starting from themselves in the center of a circle and working their way out through family, friends, acquaintances, animals, Earth, etc. The primary misunderstanding is whether the outer circles include the inner circles, i.e. whether caring for Earth includes caring for family. It’s unclear whether the subjects fully understood this, and those interpreting the results seem confused as well.
Workplace Motivation Test: “You are up for a promotion. You can be promoted into a position that pays 20% more, or one that pays the same that you’re currently making but aligns with your non-financial life goals or sense of purpose.” This one is my own, and you can learn more about the underlying concepts here: “True Believers & Mercenaries” Are you a “True Believer” or a “Mercenary”?
Need help with your interview processes or figuring out which Disney princess you are? You can find us at scalebright.ca.
-
 @ 1f9e547c:8af216ed
2024-04-23 08:56:19
@ 1f9e547c:8af216ed
2024-04-23 08:56:19testthishashtag
app.svelte-tag-default-value
-
 @ 65038d69:1fff8852
2025-03-29 12:55:20
@ 65038d69:1fff8852
2025-03-29 12:55:20Welcome to part 3 of the “What is Money?” series! So far we’ve covered the base concepts of money and money as a system in part 1, and the Canadian Dollar in part 2. Today we’re going to talk about a relatively new system of money, Bitcoin!
Let’s review a few key details about money and the Canadian Dollar (CAD). Money is a placeholder to make trading easier, so anything that can fulfill the 3 functions of money can do the job (store of value, medium of exchange, and unit of account). During the Italian Renaissance the double-entry bookkeeping (or double-entry ledger) system was codified as a method of tracking transactions, and this system is still in use today for CAD and most other money systems. One of the features of using a ledger instead of physical money with intrinsic value (such as precious metals) is that it allows for fiat (money by decree) that isn’t backed by anything. The CAD is a fully fiat money with no reserve requirements. It’s also mostly digital, with only 7% of the total supply being cash and liquid deposits with the Bank of Canada.
Bitcoin was invented by Satoshi Nakamoto, a pseudonymous individual or group who no one knows the real identity of. They released the Bitcoin whitepaper (which can be read here: https://bitcoin.org/bitcoin.pdf) in October of 2008, and on January 3, 2009 they started the Bitcoin system. 2 years later they decided to disappear and were never heard from again. Others were involved in early development and maintenance, including Laszlo Hanyecz, who completed the first real-world purchase using Bitcoin. He paid 10,000 bitcoin for 2 pizzas on May 22, 2010, which is now unofficially celebrated as “Bitcoin Pizza Day”. There are several websites and pages dedicated to the story and tracking the current “value” of those pizzas; one can be found here: https://bitcoinpizzaindex.net
Fun history nuggets aside, Bitcoin is similar to CAD in that it uses the same double-entry ledger concept. The difference is that Bitcoin uses a single digital ledger across the entire network. Transactions are grouped into 10-minute blocks and chained together, which is where the popular term “blockchain” comes from. Another term you’ve probably heard, “mining”, is all of the computers dedicated to the task competing with each other in a combination math and guessing game for who gets to verify the authenticity and correctness of each block (the combined computational power from all of the competing computers is used, not just the winner), and the winner is rewarded with newly generated bitcoin and the transaction fees from the included transactions. This is what keeps the ledger secure and makes it practically impossible to fake, break, steal, or cheat on Bitcoin transactions. Last piece of technical background, I promise: If Bitcoin is just a ledger, how do you actually “hold” the money? You do so by holding something called a “private key”. This key is used to authorize new transactions (spending the money). Think of the private key as similar to a password, PIN, or secret code for a bank account. In Bitcoin, if you hold the keys, you hold the coins.
That was a lot of history and technical stuff; take a break, touch some grass, pet the dog, sip some coffee, and come back in a few minutes.
Since you have an understanding of how money systems and CAD works I won’t bother re-explaining it all for Bitcoin; I’ll instead hit some of the major differences between it and CAD (and most other fiat currencies). Bitcoin doesn’t have a central bank or any other central authority governing or controlling it. The ledger is the “single source of truth” and anyone with a valid private key and internet connection cannot be stopped from creating a new transaction. The ledger is also fully public; you can download a full copy and view it, or use a handy website. There are several; here’s the “Bitcoin Pizza” transaction on one of my favourite public sites, mempool.space: https://mempool.space/tx/a1075db55d416d3ca199f55b6084e2115b9345e16c5cf302fc80e9d5fbf5d48d
There’s also a hard limit to the number of Bitcoin that can exist, so there’s no inflation. 21 million bitcoin, which can be divided down into 2.1 quadrillion “satoshis”, or “sats”. Think of sats as similar to the CAD penny, the smallest unit of measurement.
Bitcoin is what I call a “push” system, which is opposite of CAD’s mostly “pull” system. When you do a debit, credit card, or cheque transaction, you’re authorizing the receiving bank to reach in and “pull” the money from your account. Credit cards especially rely on this; it’s how recurring subscriptions where you are charged automatically work. Central authorities also have the ability to pull from your accounts, such as banks for fees and the Canada Revenue Agency (CRA) for taxes (though the latter pinky-promise to only do this in emergency situations). With cash, you can’t authorize someone to physically reach into your pocket and take some of your money, and it's the same with Bitcoin. You have to “push” the money to the other person. This is one of the reasons Bitcoin has been referred to as “digital cash”.
Lastly, you may have heard some, including myself, talk about Bitcoin as a replacement for fiat currencies. How is it supposed to do that if we’re required by law to use CAD? My opinion is that we’ll most likely use both for several reasons, but let’s address CAD’s requirement of use. There are no Canadian laws that force the acceptance of CAD, including cash, for purchases. In Canada cash is “legal tender”, which is “the money approved in a country for paying debts.” (See the Bank of Canada page explaining this here: https://www.bankofcanada.ca/banknotes/about-legal-tender/) If there’s no debt being settled, there is no requirement to accept CAD in cash or digital form (i.e. debit or credit card). If there is debt (i.e. paying a bill for a product or service you already received) only cash (as legal tender) is required to be accepted, but payees are not required to use it. There is a bit of an exception to CAD’s non-requirement of use though; all “business” transactions (including barter and Bitcoin) are potentially taxable and therefore are required to be reported at Fair Market Value, denominated in CAD, to the CRA. See the CRA interpretation bulletin here: https://www.canada.ca/en/revenue-agency/services/forms-publications/publications/it490/archived-barter-transactions.html Taxes are required to be paid in CAD as well.
If you’d like to see how Bitcoin works in the real world, I’d be happy to show you. I’ll even gift you a few sats to practice with! You can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-29 12:53:57
@ 65038d69:1fff8852
2025-03-29 12:53:57If you haven’t had the experience of waking up in the morning and fearing going to work, you’ve probably heard at least one story of someone who has. Someone who was afraid of their boss, a coworker, an impending audit, or layoffs. These stories are centered around fear, but what about fear’s older, more mature cousin, respect? How are they related, and what are their roles in the workplace?
Fear? Having a role in the workplace? I thought fear was bad and to be avoided at all costs? Didn’t we leave fear at work behind in the 1950s along with day-drinking and open misogyny? Not entirely it seems, but the fear we’re talking about today is of a different kind, a healthy kind. For example, a primary school child would have a healthy fear of bears. What about respect? While the term might feel dated in our current hyper-equality society, it too has a healthy version. As our example child matures, their fear of bears will develop into respect for them. They’ll understand their destructive power, but also that they’ll generally only engage it in defence. For another example, think back to your relationship with your childhood friend’s parents. As a child in an unknown adult’s home with different rules and expectations there was an amount of fear involved, but as an adult you most likely have respect for the amount of shenanigans they put up with at the hands of your and your friends.
Fear, even the unhealthy kind, can sometimes be leveraged for good. Fear of being yelled at might motivate you to finish the last 10% of a project or emptying your inbox before the end of the workday. It is better matured into respect whenever possible, however. The trade-off of fear of verbal assault or firing isn’t worth it. It’d be much healthier to be motivated by respect. Respect for your coworkers (who might also be made late by your procrastinations), your boss (who may need to take responsibility for the delay), and customers or clients (imagine yourself in their shoes).
We’ve established that respect is good, and that fear is a sometimes-useful antecedent of it. And we can all now hear a thousand voices screaming, “but so-and-so doesn’t respect me!” or “but so-and-so doesn’t deserve respect!”. They may not be wrong, so let’s see what we can do to help promote respect. Ignoring the edge cases where some people are arrogant to the point of not respecting anyone, the most common cause I’ve witnessed isn’t a lack of respect, but a misdirection of it. Respect has a directional flow from one person to another, and ideally there are streams flowing in both directions. You respect your boss for their authority and responsibilities, and your boss respects you for your expertise and commitment. Misdirection of respect isn’t giving it where it isn’t deserved but flowing in the wrong direction. For example, a coworker is regularly late for meetings, and the meeting chair says, “Out of respect for Bill we’re going to wait for them to start the meeting.” What about their respect for everyone else’s time? Respect is flowing in the wrong direction. The same thing can happen when making decisions. “Mary has been with us the longest, so we’re going to defer to her preferences and keep the fax machine in the document transfer workflow even though it’s expensive and takes longer.” Sometimes it can even lead to putting the unqualified in positions they’re incapable of executing out of a misdirection of respect. Permission to speak is an extremely common misdirection as well; respect for someone’s “right to be heard” shouldn’t override their respect for everyone else’s time.
The solution to this chaotic storm surge of misdirected respect is simple, but difficult. Break the fourth wall and haven open discussions. Start with groups and work your way down to one-on-one as necessary. Meeting start times is an excellent place to begin as most will agree that starting on time (especially with the goal of finishing on time!) is a practical shared good. Permission to speak in meetings (especially public ones) will be a difficult tackle but is also highly relevant. If respect directionality feels too heavy to bring up at work at all, try practising at home or with friends first. Failing that, a therapist or chat AI might be options.
Want someone with a neutral or outside voice to talk about fear and respect in your workplace? You can find us at scalebright.ca.
-
 @ 28246aee:62b108ad
2023-10-17 03:03:28
@ 28246aee:62b108ad
2023-10-17 03:03:28This post was originally published on https://tftc.io by Josh Centers.
As you’re probably aware, Hollywood is completely shut down right now because both the writers and actors are on strike.
But there are a couple more strikes coming up that will affect you if they happen because they’ll shut down a great deal of our supply chain: UPS and Yellow.
Photo by Daphne Fecheyr on Unsplash
Craig Fuller, CEO of Freightwaves, said, “A Yellow shutdown (almost certain) and UPS strike would be a catastrophic/unprecedented shock to supply chains. Massive volatility, across all modes.”
If you haven’t heard of Yellow Transportation, they hold about 10% of what’s known as the less-than-truckload (LTL) business. Yellow has been hemorrhaging cash for years, and is now on the verge of bankruptcy. On top of that, the Teamsters are close to a strike—as soon as Monday—because Yellow has stopped paying into the pension fund. That has caused customers to drop Yellow, making matters even worse.
Meanwhile, the Teamsters are also butting heads with UPS, although the situation there looks somewhat more optimistic than Yellow: From The Washington Post:On Wednesday, UPS and the Teamsters, the union representing UPS workers, announced that after a two-week impasse, they had agreed to resume negotiations next week with time running out before the Aug. 1 deadline.While the two sides have resolved most of their issues, with UPS agreeing to install air conditioning in vans and eliminate a lower paid class of workers, they remain at odds over pay and benefits for part-time workers who make up more than half of UPS’s workforce.“I think it’s likely a work stoppage will occur and the key question at this point is how long it will last,” said Alan Amling, a fellow at the University of Tennessee’s Global Supply Chain Institute and a former UPS executive.
And UPS workers are already staging dress rehearsals for a strike:
As the strike deadline has neared, so-called “practice pickets,” or dress rehearsals for the potential strike, have sprung up outside UPS facilities from Hawaii to New York, with hundreds of Teamsters UPS members in brown work uniforms marching and chanting: “What do we want? Contract!”
All of this really hinges on what UPS and the Teamsters decide on in this week’s upcoming contract negotiations. While the industry is well-prepared for Yellow’s downfall, it’s not prepared for a shutdown of Yellow and UPS at the same time:
His projection of how a UPS strike would play out foresees that LTL carriers would be “flooded with freight opportunities.” Volume also would “show up” at FedEx, the U.S. Postal Service and parts of the DHL network. But the problem is that “they simply aren’t going to have the capacity” to handle the freight moving out of the UPS network.
Bottom line: if you have anything sitting in your online shopping carts, now would be a good time to buy it.
And if you’re a trucker or mechanic in the business, Freight Waves has advice on how to prepare your shipping company going bankrupt. If you work for Yellow, take your tools home now!
Article was originally from unprepared.life
-
 @ 65038d69:1fff8852
2025-03-29 12:46:30
@ 65038d69:1fff8852
2025-03-29 12:46:30In part 1 of this series (Part 1 - What is Money?) we overviewed the history of money and as a global concept. Now that we have a base understanding of what money is we can get into detail about the Canadian Dollar. Why the Canadian Dollar specifically? One of the inspirations for this series was realizing how much the pervasiveness of American media has affected the average Canadian’s understanding of how our money works. How many of you can quote what is printed on US bills? Do you know what is printed on Canadian bills? What about what the Canadian Dollar is backed by, and who’s in charge of it? To preview, it’s not gold, and it’s not the Federal Reserve.
Lets do some history to give us some background on the Canadian Dollar (CAD) as we know it today. In 1858 the Province of Canada introduced the Canadian Dollar as a hopeful replacement for the mix of British, American, Spanish, and private bank credit notes in use. In 1867 Canada was formed as a nation, and the next year the Government of Canada issued Dominion credit notes as currency. These Dominion notes were required to be backed by a minimum of 20% gold reserves. This is called a “fractional reserve” system, or fractional reserve banking. Reserve requirements for private bank notes and Dominion notes changed over the years leading up to 1935 when the Bank of Canada (BoC) was formed and became to sole issuer of currency in Canada. 10 years later gold reserve requirements were removed and the Dollar became a fully fiat currency (remember this term from the previous article?).
The Bank of Canada is Canada’s “central bank”. If you check out the About Us page on their website (https://www.bankofcanada.ca/about/) you’ll see they have a broad range of roles and responsibilities, but the main one we’re focused on is that they manage the Canadian Dollar as a system of money, including creating and destroying Dollars as they deem necessary. (This is similar to the American Federal Reserve, but a key difference is that the BoC is a crown corporation, while the Federal Reserve is owned by private banks.) The creation and destruction of Dollars is a complex process, but it’s mostly done through borrowing. The government indirectly borrows money from the BoC (and sometimes directly from commercial banks), and everyone else borrows from banks. This money is then created by the BoC and banks, and when the principal (debt exclusive of interest) is paid back, its destroyed.
I’d be remiss if I didn’t mention and define “inflation”, “monetary expansion”, and the “Quantity Theory of Money”. The BoC defines inflation as “…a persistent rise in the average level of prices over time.” They have an excellent explainer on their website here (https://www.bankofcanada.ca/2020/08/understanding-inflation/); to summarize, the BoC and government use the Consumer Price Index (CPI) to keep track of this. “Monetary expansion” is when money is created and kept in circulation. The “Quantity Theory of Money” states that when new money is created it becomes less valuable, which means prices increase, AKA inflation. With this in mind the BoC targets a 2% inflation rate when making decisions about creating and destroying Dollars (through the systems of borrowing). Whether they’re successful or not is the subject of an article all on its own and much speculation.
I should also mention an outlier in the Canadian financial system; Credit Unions. These are provincial banks that don’t have a direct relationship with the BoC. They’re generally much smaller than the national banks and offer fewer services, but many feel they offer a more personal service. And one credit union in particular is an outlier among outliers; Bow Valley Credit Union in Alberta. They’ve embarked on mission to stockpile precious metals (mostly gold) as a form of guarantee for customer deposits. They still practice fractional reserve banking, but this is an improvement over zero reserve banking.
You might be imagining stacks of Dollar notes being passed around all these institutions, but most of the money only exists in ledgers (remember this from part 1?). For comparison, there is currently about $250B in the M0 supply (liquid deposits at the BoC and cash), and the rest totals about $3500B, or $3.5T. That’s about 7% as “real” money that could be used to buy groceries or for payroll. To move this invisible money around the government created Payments Canada, a non-profit that operates most of the inter-institution transfer systems. (They have other responsibilities as well.) Lynx and the Automated Clearing Settlement System (ACSS) are currently in use, and Real-Time Rail (RTR) is coming soon to augment them.
On the retail side, we have the Interac network and credit card networks. The Interac Corporation (a for-profit founded and primarily owned by major national banks) operates the Interac network, which is the primary debit card network in Canada, as well as Interac e-Transfer for direct electronic payments. Visa and Mastercard are the primary credit card networks, but they simply move payment information between banks and Payment Services Providers (PSPs). PSPs are responsible for the actual payment settlements. You’ve probably heard of some of the major ones; Moneris, Chase, Square, and PayPal to name a few. If that sounds complicated, that’s because it is. Let’s walk through an example credit card payment at a physical store to see how it works. The customer inserts, taps, or swipes their card at the payment terminal, typically managed by a Point of Sale (POS) provider. The terminal sends the information to the PSP, who sends the information through the credit card network to the issuing bank. If the transaction is approved, it’s logged for transfer in a batch later, and the approval makes it way back through the credit card network, PSP, terminal, and POS.
Wipe the sweat from your brow and take a sip of coffee; that was a lot! The important part to remember is that all of this complexity serves to move numbers between accounts in ledgers. The government (through the BoC) controls the money supply (the primary driver of inflation), and the banks and networks move the ledger numbers between individuals, companies, and each other. About 7% is liquid, and 0% is backed by hard assets such as gold.
In part 3 we’ll cover Bitcoin, its intention to replace fiat currencies, and its current state in Canada.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:23:35
@ 91bea5cd:1df4451c
2025-04-15 06:23:35Um bom gerenciamento de senhas deve ser simples e seguir a filosofia do Unix. Organizado em hierarquia e fácil de passar de um computador para outro.
E por isso não é recomendável o uso de aplicativos de terceiros que tenham acesso a suas chaves(senhas) em seus servidores, tampouco as opções nativas dos navegadores, que também pertencem a grandes empresas que fazem um grande esforço para ter acesso a nossas informações.
Recomendação
- pass
- Qtpass (gerenciador gráfico)
Com ele seus dados são criptografados usando sua chave gpg e salvo em arquivos organizados por pastas de forma hierárquica, podendo ser integrado a um serviço git de sua escolha ou copiado facilmente de um local para outro.
Uso
O seu uso é bem simples.
Configuração:
pass git initPara ver:
pass Email/example.comCopiar para área de transferência (exige xclip):
pass -c Email/example.comPara inserir:
pass insert Email/example0.comPara inserir e gerar senha:
pass generate Email/example1.comPara inserir e gerar senha sem símbolos:
pass generate --no-symbols Email/example1.comPara inserir, gerar senha e copiar para área de transferência :
pass generate -c Email/example1.comPara remover:
pass rm Email/example.com -
 @ 91bea5cd:1df4451c
2025-04-15 06:19:19
@ 91bea5cd:1df4451c
2025-04-15 06:19:19O que é Tahoe-LAFS?
Bem-vindo ao Tahoe-LAFS_, o primeiro sistema de armazenamento descentralizado com
- Segurança independente do provedor * .
Tahoe-LAFS é um sistema que ajuda você a armazenar arquivos. Você executa um cliente Programa no seu computador, que fala com um ou mais servidores de armazenamento em outros computadores. Quando você diz ao seu cliente para armazenar um arquivo, ele irá criptografar isso Arquivo, codifique-o em múltiplas peças, depois espalhe essas peças entre Vários servidores. As peças são todas criptografadas e protegidas contra Modificações. Mais tarde, quando você pede ao seu cliente para recuperar o arquivo, ele irá Encontre as peças necessárias, verifique se elas não foram corrompidas e remontadas Eles, e descriptografar o resultado.
O cliente cria mais peças (ou "compartilhamentos") do que acabará por precisar, então Mesmo que alguns servidores falhem, você ainda pode recuperar seus dados. Corrompido Os compartilhamentos são detectados e ignorados, de modo que o sistema pode tolerar o lado do servidor Erros no disco rígido. Todos os arquivos são criptografados (com uma chave exclusiva) antes Uploading, então mesmo um operador de servidor mal-intencionado não pode ler seus dados. o A única coisa que você pede aos servidores é que eles podem (geralmente) fornecer o Compartilha quando você os solicita: você não está confiando sobre eles para Confidencialidade, integridade ou disponibilidade absoluta.
O que é "segurança independente do provedor"?
Todo vendedor de serviços de armazenamento na nuvem irá dizer-lhe que o seu serviço é "seguro". Mas o que eles significam com isso é algo fundamentalmente diferente Do que queremos dizer. O que eles significam por "seguro" é que depois de ter dado Eles o poder de ler e modificar seus dados, eles tentam muito difícil de não deixar Esse poder seja abusado. Isso acaba por ser difícil! Insetos, Configurações incorretas ou erro do operador podem acidentalmente expor seus dados para Outro cliente ou para o público, ou pode corromper seus dados. Criminosos Ganho rotineiramente de acesso ilícito a servidores corporativos. Ainda mais insidioso é O fato de que os próprios funcionários às vezes violam a privacidade do cliente De negligência, avareza ou mera curiosidade. O mais consciencioso de Esses prestadores de serviços gastam consideráveis esforços e despesas tentando Mitigar esses riscos.
O que queremos dizer com "segurança" é algo diferente. * O provedor de serviços Nunca tem a capacidade de ler ou modificar seus dados em primeiro lugar: nunca. * Se você usa Tahoe-LAFS, então todas as ameaças descritas acima não são questões para você. Não só é fácil e barato para o provedor de serviços Manter a segurança de seus dados, mas na verdade eles não podem violar sua Segurança se eles tentaram. Isto é o que chamamos de * independente do fornecedor segurança*.
Esta garantia está integrada naturalmente no sistema de armazenamento Tahoe-LAFS e Não exige que você execute um passo de pré-criptografia manual ou uma chave complicada gestão. (Afinal, ter que fazer operações manuais pesadas quando Armazenar ou acessar seus dados anularia um dos principais benefícios de Usando armazenamento em nuvem em primeiro lugar: conveniência.)
Veja como funciona:
Uma "grade de armazenamento" é constituída por uma série de servidores de armazenamento. Um servidor de armazenamento Tem armazenamento direto em anexo (tipicamente um ou mais discos rígidos). Um "gateway" Se comunica com os nós de armazenamento e os usa para fornecer acesso ao Rede sobre protocolos como HTTP (S), SFTP ou FTP.
Observe que você pode encontrar "cliente" usado para se referir aos nós do gateway (que atuam como Um cliente para servidores de armazenamento) e também para processos ou programas que se conectam a Um nó de gateway e operações de execução na grade - por exemplo, uma CLI Comando, navegador da Web, cliente SFTP ou cliente FTP.
Os usuários não contam com servidores de armazenamento para fornecer * confidencialidade * nem
- Integridade * para seus dados - em vez disso, todos os dados são criptografados e Integridade verificada pelo gateway, para que os servidores não possam ler nem Modifique o conteúdo dos arquivos.
Os usuários dependem de servidores de armazenamento para * disponibilidade *. O texto cifrado é Codificado por apagamento em partes
Ndistribuídas em pelo menosHdistintas Servidores de armazenamento (o valor padrão paraNé 10 e paraHé 7) então Que pode ser recuperado de qualquerKdesses servidores (o padrão O valor deKé 3). Portanto, apenas a falha doH-K + 1(com o Padrões, 5) servidores podem tornar os dados indisponíveis.No modo de implantação típico, cada usuário executa seu próprio gateway sozinho máquina. Desta forma, ela confia em sua própria máquina para a confidencialidade e Integridade dos dados.
Um modo de implantação alternativo é que o gateway é executado em uma máquina remota e O usuário se conecta ao HTTPS ou SFTP. Isso significa que o operador de O gateway pode visualizar e modificar os dados do usuário (o usuário * depende de * o Gateway para confidencialidade e integridade), mas a vantagem é que a O usuário pode acessar a grade Tahoe-LAFS com um cliente que não possui o Software de gateway instalado, como um quiosque de internet ou celular.
Controle de acesso
Existem dois tipos de arquivos: imutáveis e mutáveis. Quando você carrega um arquivo Para a grade de armazenamento, você pode escolher o tipo de arquivo que será no grade. Os arquivos imutáveis não podem ser modificados quando foram carregados. UMA O arquivo mutable pode ser modificado por alguém com acesso de leitura e gravação. Um usuário Pode ter acesso de leitura e gravação a um arquivo mutable ou acesso somente leitura, ou não Acesso a ele.
Um usuário que tenha acesso de leitura e gravação a um arquivo mutable ou diretório pode dar Outro acesso de leitura e gravação do usuário a esse arquivo ou diretório, ou eles podem dar Acesso somente leitura para esse arquivo ou diretório. Um usuário com acesso somente leitura Para um arquivo ou diretório pode dar acesso a outro usuário somente leitura.
Ao vincular um arquivo ou diretório a um diretório pai, você pode usar um Link de leitura-escrita ou um link somente de leitura. Se você usar um link de leitura e gravação, então Qualquer pessoa que tenha acesso de leitura e gravação ao diretório pai pode obter leitura-escrita Acesso à criança e qualquer pessoa que tenha acesso somente leitura ao pai O diretório pode obter acesso somente leitura à criança. Se você usar uma leitura somente Link, qualquer pessoa que tenha lido-escrito ou acesso somente leitura ao pai O diretório pode obter acesso somente leitura à criança.
================================================== ==== Usando Tahoe-LAFS com uma rede anônima: Tor, I2P ================================================== ====
. `Visão geral '
. `Casos de uso '
.
Software Dependencies_#.
Tor#.I2P. `Configuração de conexão '
. `Configuração de Anonimato '
#.
Anonimato do cliente ' #.Anonimato de servidor, configuração manual ' #. `Anonimato de servidor, configuração automática '. `Problemas de desempenho e segurança '
Visão geral
Tor é uma rede anonimização usada para ajudar a esconder a identidade da Internet Clientes e servidores. Consulte o site do Tor Project para obter mais informações: Https://www.torproject.org/
I2P é uma rede de anonimato descentralizada que se concentra no anonimato de ponta a ponta Entre clientes e servidores. Consulte o site I2P para obter mais informações: Https://geti2p.net/
Casos de uso
Existem três casos de uso potenciais para Tahoe-LAFS do lado do cliente:
-
O usuário deseja sempre usar uma rede de anonimato (Tor, I2P) para proteger Seu anonimato quando se conecta às redes de armazenamento Tahoe-LAFS (seja ou Não os servidores de armazenamento são anônimos).
-
O usuário não se preocupa em proteger seu anonimato, mas eles desejam se conectar a Servidores de armazenamento Tahoe-LAFS que são acessíveis apenas através de Tor Hidden Services ou I2P.
-
Tor é usado apenas se uma sugestão de conexão do servidor usar
tor:. Essas sugestões Geralmente tem um endereço.onion. -
I2P só é usado se uma sugestão de conexão do servidor usa
i2p:. Essas sugestões Geralmente têm um endereço.i2p. -
O usuário não se preocupa em proteger seu anonimato ou para se conectar a um anonimato Servidores de armazenamento. Este documento não é útil para você ... então pare de ler.
Para servidores de armazenamento Tahoe-LAFS existem três casos de uso:
-
O operador deseja proteger o anonimato fazendo seu Tahoe Servidor acessível apenas em I2P, através de Tor Hidden Services, ou ambos.
-
O operador não * requer * anonimato para o servidor de armazenamento, mas eles Quer que ele esteja disponível tanto no TCP / IP roteado publicamente quanto através de um Rede de anonimização (I2P, Tor Hidden Services). Uma possível razão para fazer Isso é porque ser alcançável através de uma rede de anonimato é um Maneira conveniente de ignorar NAT ou firewall que impede roteios públicos Conexões TCP / IP ao seu servidor (para clientes capazes de se conectar a Tais servidores). Outro é o que torna o seu servidor de armazenamento acessível Através de uma rede de anonimato pode oferecer uma melhor proteção para sua Clientes que usam essa rede de anonimato para proteger seus anonimato.
-
O operador do servidor de armazenamento não se preocupa em proteger seu próprio anonimato nem Para ajudar os clientes a proteger o deles. Pare de ler este documento e execute Seu servidor de armazenamento Tahoe-LAFS usando TCP / IP com roteamento público.
Veja esta página do Tor Project para obter mais informações sobre Tor Hidden Services: Https://www.torproject.org/docs/hidden-services.html.pt
Veja esta página do Projeto I2P para obter mais informações sobre o I2P: Https://geti2p.net/en/about/intro
Dependências de software
Tor
Os clientes que desejam se conectar a servidores baseados em Tor devem instalar o seguinte.
-
Tor (tor) deve ser instalado. Veja aqui: Https://www.torproject.org/docs/installguide.html.en. No Debian / Ubuntu, Use
apt-get install tor. Você também pode instalar e executar o navegador Tor Agrupar. -
Tahoe-LAFS deve ser instalado com o
[tor]"extra" habilitado. Isso vai Instaletxtorcon::
Pip install tahoe-lafs [tor]
Os servidores Tor-configurados manualmente devem instalar Tor, mas não precisam
Txtorconou o[tor]extra. Configuração automática, quando Implementado, vai precisar destes, assim como os clientes.I2P
Os clientes que desejam se conectar a servidores baseados em I2P devem instalar o seguinte. Tal como acontece com Tor, os servidores baseados em I2P configurados manualmente precisam do daemon I2P, mas Não há bibliotecas especiais de apoio Tahoe-side.
-
I2P deve ser instalado. Veja aqui: Https://geti2p.net/en/download
-
A API SAM deve estar habilitada.
-
Inicie o I2P.
- Visite http://127.0.0.1:7657/configclients no seu navegador.
- Em "Configuração do Cliente", marque a opção "Executar no Startup?" Caixa para "SAM Ponte de aplicação ".
- Clique em "Salvar Configuração do Cliente".
-
Clique no controle "Iniciar" para "ponte de aplicação SAM" ou reinicie o I2P.
-
Tahoe-LAFS deve ser instalado com o
[i2p]extra habilitado, para obterTxi2p::
Pip install tahoe-lafs [i2p]
Tor e I2P
Os clientes que desejam se conectar a servidores baseados em Tor e I2P devem instalar tudo acima. Em particular, Tahoe-LAFS deve ser instalado com ambos Extras habilitados ::
Pip install tahoe-lafs [tor, i2p]
Configuração de conexão
Consulte: ref:
Connection Managementpara uma descrição do[tor]e[I2p]seções detahoe.cfg. Estes controlam como o cliente Tahoe Conecte-se a um daemon Tor / I2P e, assim, faça conexões com Tor / I2P-baseadas Servidores.As seções
[tor]e[i2p]só precisam ser modificadas para serem usadas de forma incomum Configurações ou para habilitar a configuração automática do servidor.A configuração padrão tentará entrar em contato com um daemon local Tor / I2P Ouvindo as portas usuais (9050/9150 para Tor, 7656 para I2P). Enquanto Há um daemon em execução no host local e o suporte necessário Bibliotecas foram instaladas, os clientes poderão usar servidores baseados em Tor Sem qualquer configuração especial.
No entanto, note que esta configuração padrão não melhora a Anonimato: as conexões TCP normais ainda serão feitas em qualquer servidor que Oferece um endereço regular (cumpre o segundo caso de uso do cliente acima, não o terceiro). Para proteger o anonimato, os usuários devem configurar o
[Connections]da seguinte maneira:[Conexões] Tcp = tor
Com isso, o cliente usará Tor (em vez de um IP-address -reviração de conexão direta) para alcançar servidores baseados em TCP.
Configuração de anonimato
Tahoe-LAFS fornece uma configuração "flag de segurança" para indicar explicitamente Seja necessário ou não a privacidade do endereço IP para um nó ::
[nó] Revelar-IP-address = (booleano, opcional)
Quando
revelar-IP-address = False, Tahoe-LAFS se recusará a iniciar se algum dos As opções de configuração emtahoe.cfgrevelariam a rede do nó localização:-
[Conexões] tcp = toré necessário: caso contrário, o cliente faria Conexões diretas para o Introdução, ou qualquer servidor baseado em TCP que aprende Do Introdutor, revelando seu endereço IP para esses servidores e um Rede de espionagem. Com isso, Tahoe-LAFS só fará Conexões de saída através de uma rede de anonimato suportada. -
Tub.locationdeve ser desativado ou conter valores seguros. este O valor é anunciado para outros nós através do Introdutor: é como um servidor Anuncia sua localização para que os clientes possam se conectar a ela. No modo privado, ele É um erro para incluir umtcp:dica notub.location. Modo privado Rejeita o valor padrão detub.location(quando a chave está faltando Inteiramente), que éAUTO, que usaifconfigpara adivinhar o nó Endereço IP externo, o que o revelaria ao servidor e a outros clientes.
Esta opção é ** crítica ** para preservar o anonimato do cliente (cliente Caso de uso 3 de "Casos de uso", acima). Também é necessário preservar uma Anonimato do servidor (caso de uso do servidor 3).
Esse sinalizador pode ser configurado (para falso), fornecendo o argumento
--hide-ippara Os comandoscreate-node,create-clientoucreate-introducer.Observe que o valor padrão de
revelar-endereço IPé verdadeiro, porque Infelizmente, esconder o endereço IP do nó requer software adicional para ser Instalado (conforme descrito acima) e reduz o desempenho.Anonimato do cliente
Para configurar um nó de cliente para anonimato,
tahoe.cfg** deve ** conter o Seguindo as bandeiras de configuração ::[nó] Revelar-IP-address = False Tub.port = desativado Tub.location = desativado
Uma vez que o nodo Tahoe-LAFS foi reiniciado, ele pode ser usado anonimamente (cliente Caso de uso 3).
Anonimato do servidor, configuração manual
Para configurar um nó de servidor para ouvir em uma rede de anonimato, devemos primeiro Configure Tor para executar um "Serviço de cebola" e encaminhe as conexões de entrada para o Porto Tahoe local. Então, configuramos Tahoe para anunciar o endereço
.onionAos clientes. Também configuramos Tahoe para não fazer conexões TCP diretas.- Decida em um número de porta de escuta local, chamado PORT. Isso pode ser qualquer não utilizado Porta de cerca de 1024 até 65535 (dependendo do kernel / rede do host Config). Nós diremos a Tahoe para escutar nesta porta, e nós diremos a Tor para Encaminhe as conexões de entrada para ele.
- Decida em um número de porta externo, chamado VIRTPORT. Isso será usado no Localização anunciada e revelada aos clientes. Pode ser qualquer número de 1 Para 65535. Pode ser o mesmo que PORT, se quiser.
- Decida em um "diretório de serviço oculto", geralmente em
/ var / lib / tor / NAME. Pediremos a Tor para salvar o estado do serviço de cebola aqui, e Tor irá Escreva o endereço.onionaqui depois que ele for gerado.
Em seguida, faça o seguinte:
-
Crie o nó do servidor Tahoe (com
tahoe create-node), mas não ** não ** Lança-o ainda. -
Edite o arquivo de configuração Tor (normalmente em
/ etc / tor / torrc). Precisamos adicionar Uma seção para definir o serviço oculto. Se nossa PORT for 2000, VIRTPORT é 3000, e estamos usando/ var / lib / tor / tahoecomo o serviço oculto Diretório, a seção deve se parecer com ::HiddenServiceDir / var / lib / tor / tahoe HiddenServicePort 3000 127.0.0.1:2000
-
Reinicie Tor, com
systemctl restart tor. Aguarde alguns segundos. -
Leia o arquivo
hostnameno diretório de serviço oculto (por exemplo,/ Var / lib / tor / tahoe / hostname). Este será um endereço.onion, comoU33m4y7klhz3b.onion. Ligue para esta CEBOLA. -
Edite
tahoe.cfgpara configurartub.portpara usarTcp: PORT: interface = 127.0.0.1etub.locationpara usarTor: ONION.onion: VIRTPORT. Usando os exemplos acima, isso seria ::[nó] Revelar-endereço IP = falso Tub.port = tcp: 2000: interface = 127.0.0.1 Tub.location = tor: u33m4y7klhz3b.onion: 3000 [Conexões] Tcp = tor
-
Inicie o servidor Tahoe com
tahoe start $ NODEDIR
A seção
tub.portfará com que o servidor Tahoe ouça no PORT, mas Ligue o soquete de escuta à interface de loopback, que não é acessível Do mundo exterior (mas * é * acessível pelo daemon Tor local). Então o A seçãotcp = torfaz com que Tahoe use Tor quando se conecta ao Introdução, escondendo o endereço IP. O nó se anunciará a todos Clientes que usam `tub.location``, então os clientes saberão que devem usar o Tor Para alcançar este servidor (e não revelar seu endereço IP através do anúncio). Quando os clientes se conectam ao endereço da cebola, seus pacotes serão Atravessar a rede de anonimato e eventualmente aterrar no Tor local Daemon, que então estabelecerá uma conexão com PORT no localhost, que é Onde Tahoe está ouvindo conexões.Siga um processo similar para construir um servidor Tahoe que escuta no I2P. o O mesmo processo pode ser usado para ouvir tanto o Tor como o I2P (
tub.location = Tor: ONION.onion: VIRTPORT, i2p: ADDR.i2p). Também pode ouvir tanto Tor como TCP simples (caso de uso 2), comtub.port = tcp: PORT,tub.location = Tcp: HOST: PORT, tor: ONION.onion: VIRTPORTeanonymous = false(e omite A configuraçãotcp = tor, já que o endereço já está sendo transmitido através de O anúncio de localização).Anonimato do servidor, configuração automática
Para configurar um nó do servidor para ouvir em uma rede de anonimato, crie o Nó com a opção
--listen = tor. Isso requer uma configuração Tor que Ou lança um novo daemon Tor, ou tem acesso à porta de controle Tor (e Autoridade suficiente para criar um novo serviço de cebola). Nos sistemas Debian / Ubuntu, façaApt install tor, adicione-se ao grupo de controle comadduser YOURUSERNAME debian-tore, em seguida, inicie sessão e faça o login novamente: se osgroupsO comando incluidebian-torna saída, você deve ter permissão para Use a porta de controle de domínio unix em/ var / run / tor / control.Esta opção irá definir
revelar-IP-address = Falsee[connections] tcp = Tor. Ele alocará as portas necessárias, instruirá Tor para criar a cebola Serviço (salvando a chave privada em algum lugar dentro de NODEDIR / private /), obtenha O endereço.onione preenchatub.portetub.locationcorretamente.Problemas de desempenho e segurança
Se você estiver executando um servidor que não precisa ser Anônimo, você deve torná-lo acessível através de uma rede de anonimato ou não? Ou você pode torná-lo acessível * ambos * através de uma rede de anonimato E como um servidor TCP / IP rastreável publicamente?
Existem várias compensações efetuadas por esta decisão.
Penetração NAT / Firewall
Fazer com que um servidor seja acessível via Tor ou I2P o torna acessível (por Clientes compatíveis com Tor / I2P) mesmo que existam NAT ou firewalls que impeçam Conexões TCP / IP diretas para o servidor.
Anonimato
Tornar um servidor Tahoe-LAFS acessível * somente * via Tor ou I2P pode ser usado para Garanta que os clientes Tahoe-LAFS usem Tor ou I2P para se conectar (Especificamente, o servidor só deve anunciar endereços Tor / I2P no Chave de configuração
tub.location). Isso evita que os clientes mal configurados sejam Desingonizando-se acidentalmente, conectando-se ao seu servidor através de A Internet rastreável.Claramente, um servidor que está disponível como um serviço Tor / I2P * e * a O endereço TCP regular não é anônimo: o endereço do .on e o real O endereço IP do servidor é facilmente vinculável.
Além disso, a interação, através do Tor, com um Tor Oculto pode ser mais Protegido da análise do tráfego da rede do que a interação, através do Tor, Com um servidor TCP / IP com rastreamento público
** XXX há um documento mantido pelos desenvolvedores de Tor que comprovem ou refutam essa crença? Se assim for, precisamos ligar a ele. Caso contrário, talvez devêssemos explicar mais aqui por que pensamos isso? **
Linkability
A partir de 1.12.0, o nó usa uma única chave de banheira persistente para saída Conexões ao Introdutor e conexões de entrada para o Servidor de Armazenamento (E Helper). Para os clientes, uma nova chave Tub é criada para cada servidor de armazenamento Nós aprendemos sobre, e essas chaves são * não * persistiram (então elas mudarão cada uma delas Tempo que o cliente reinicia).
Clientes que atravessam diretórios (de rootcap para subdiretório para filecap) são É provável que solicitem os mesmos índices de armazenamento (SIs) na mesma ordem de cada vez. Um cliente conectado a vários servidores irá pedir-lhes todos para o mesmo SI em Quase ao mesmo tempo. E dois clientes que compartilham arquivos ou diretórios Irá visitar os mesmos SI (em várias ocasiões).
Como resultado, as seguintes coisas são vinculáveis, mesmo com
revelar-endereço IP = Falso:- Servidores de armazenamento podem vincular reconhecer várias conexões do mesmo Cliente ainda não reiniciado. (Observe que o próximo recurso de Contabilidade pode Faz com que os clientes apresentem uma chave pública persistente do lado do cliente quando Conexão, que será uma ligação muito mais forte).
- Os servidores de armazenamento provavelmente podem deduzir qual cliente está acessando dados, por Olhando as SIs sendo solicitadas. Vários servidores podem conciliar Determine que o mesmo cliente está falando com todos eles, mesmo que o TubIDs são diferentes para cada conexão.
- Os servidores de armazenamento podem deduzir quando dois clientes diferentes estão compartilhando dados.
- O Introdutor pode entregar diferentes informações de servidor para cada um Cliente subscrito, para particionar clientes em conjuntos distintos de acordo com Quais as conexões do servidor que eles eventualmente fazem. Para clientes + nós de servidor, ele Também pode correlacionar o anúncio do servidor com o cliente deduzido identidade.
atuação
Um cliente que se conecta a um servidor Tahoe-LAFS com rastreamento público através de Tor Incorrem em latência substancialmente maior e, às vezes, pior Mesmo cliente se conectando ao mesmo servidor através de um TCP / IP rastreável normal conexão. Quando o servidor está em um Tor Hidden Service, ele incorre ainda mais Latência e, possivelmente, ainda pior rendimento.
Conectando-se a servidores Tahoe-LAFS que são servidores I2P incorrem em maior latência E pior rendimento também.
Efeitos positivos e negativos em outros usuários Tor
O envio de seu tráfego Tahoe-LAFS sobre o Tor adiciona tráfego de cobertura para outros Tor usuários que também estão transmitindo dados em massa. Então isso é bom para Eles - aumentando seu anonimato.
No entanto, torna o desempenho de outros usuários do Tor Sessões - por exemplo, sessões ssh - muito pior. Isso é porque Tor Atualmente não possui nenhuma prioridade ou qualidade de serviço Recursos, para que as teclas de Ssh de outra pessoa possam ter que esperar na fila Enquanto o conteúdo do arquivo em massa é transmitido. O atraso adicional pode Tornar as sessões interativas de outras pessoas inutilizáveis.
Ambos os efeitos são duplicados se você carregar ou baixar arquivos para um Tor Hidden Service, em comparação com se você carregar ou baixar arquivos Over Tor para um servidor TCP / IP com rastreamento público
Efeitos positivos e negativos em outros usuários do I2P
Enviar seu tráfego Tahoe-LAFS ao I2P adiciona tráfego de cobertura para outros usuários do I2P Que também estão transmitindo dados. Então, isso é bom para eles - aumentando sua anonimato. Não prejudicará diretamente o desempenho de outros usuários do I2P Sessões interativas, porque a rede I2P possui vários controles de congestionamento e Recursos de qualidade de serviço, como priorizar pacotes menores.
No entanto, se muitos usuários estão enviando tráfego Tahoe-LAFS ao I2P e não tiverem Seus roteadores I2P configurados para participar de muito tráfego, então o I2P A rede como um todo sofrerá degradação. Cada roteador Tahoe-LAFS que usa o I2P tem Seus próprios túneis de anonimato que seus dados são enviados. Em média, um O nó Tahoe-LAFS requer 12 outros roteadores I2P para participar de seus túneis.
Portanto, é importante que o seu roteador I2P esteja compartilhando a largura de banda com outros Roteadores, para que você possa retornar enquanto usa o I2P. Isso nunca prejudicará a Desempenho de seu nó Tahoe-LAFS, porque seu roteador I2P sempre Priorize seu próprio tráfego.
=========================
Como configurar um servidor
Muitos nós Tahoe-LAFS são executados como "servidores", o que significa que eles fornecem serviços para Outras máquinas (isto é, "clientes"). Os dois tipos mais importantes são os Introdução e Servidores de armazenamento.
Para ser útil, os servidores devem ser alcançados pelos clientes. Os servidores Tahoe podem ouvir Em portas TCP e anunciar sua "localização" (nome do host e número da porta TCP) Para que os clientes possam se conectar a eles. Eles também podem ouvir os serviços de cebola "Tor" E portas I2P.
Os servidores de armazenamento anunciam sua localização ao anunciá-lo ao Introdutivo, Que então transmite a localização para todos os clientes. Então, uma vez que a localização é Determinado, você não precisa fazer nada de especial para entregá-lo.
O próprio apresentador possui uma localização, que deve ser entregue manualmente a todos Servidores de armazenamento e clientes. Você pode enviá-lo para os novos membros do seu grade. Esta localização (juntamente com outros identificadores criptográficos importantes) é Escrito em um arquivo chamado
private / introducer.furlno Presenter's Diretório básico, e deve ser fornecido como o argumento--introducer =paraTahoe create-nodeoutahoe create-node.O primeiro passo ao configurar um servidor é descobrir como os clientes irão alcançar. Então você precisa configurar o servidor para ouvir em algumas portas, e Depois configure a localização corretamente.
Configuração manual
Cada servidor tem duas configurações em seu arquivo
tahoe.cfg:tub.port, eTub.location. A "porta" controla o que o nó do servidor escuta: isto Geralmente é uma porta TCP.A "localização" controla o que é anunciado para o mundo exterior. Isto é um "Sugestão de conexão foolscap", e inclui tanto o tipo de conexão (Tcp, tor ou i2p) e os detalhes da conexão (nome do host / endereço, porta número). Vários proxies, gateways e redes de privacidade podem ser Envolvido, então não é incomum para
tub.portetub.locationpara olhar diferente.Você pode controlar diretamente a configuração
tub.portetub.locationConfigurações, fornecendo--port =e--location =ao executartahoe Create-node.Configuração automática
Em vez de fornecer
--port = / - location =, você pode usar--listen =. Os servidores podem ouvir em TCP, Tor, I2P, uma combinação desses ou nenhum. O argumento--listen =controla quais tipos de ouvintes o novo servidor usará.--listen = nonesignifica que o servidor não deve ouvir nada. Isso não Faz sentido para um servidor, mas é apropriado para um nó somente cliente. o O comandotahoe create-clientinclui automaticamente--listen = none.--listen = tcpé o padrão e liga uma porta de escuta TCP padrão. Usar--listen = tcprequer um argumento--hostname =também, que será Incorporado no local anunciado do nó. Descobrimos que os computadores Não pode determinar de forma confiável seu nome de host acessível externamente, então, em vez de Ter o servidor adivinhar (ou escanear suas interfaces para endereços IP Isso pode ou não ser apropriado), a criação de nó requer que o usuário Forneça o nome do host.--listen = torconversará com um daemon Tor local e criará uma nova "cebola" Servidor "(que se parece comalzrgrdvxct6c63z.onion).--listen = i2p` conversará com um daemon I2P local e criará um novo servidor endereço. Consulte: doc:anonymity-configuration` para obter detalhes.Você pode ouvir nos três usando
--listen = tcp, tor, i2p.Cenários de implantação
A seguir, alguns cenários sugeridos para configurar servidores usando Vários transportes de rede. Estes exemplos não incluem a especificação de um Apresentador FURL que normalmente você gostaria quando provisionamento de armazenamento Nós. Para estes e outros detalhes de configuração, consulte : Doc:
configuration.. `Servidor possui um nome DNS público '
.
Servidor possui um endereço público IPv4 / IPv6_.
O servidor está por trás de um firewall com encaminhamento de porta_.
Usando o I2P / Tor para evitar o encaminhamento da porta_O servidor possui um nome DNS público
O caso mais simples é o local onde o host do servidor está diretamente conectado ao Internet, sem um firewall ou caixa NAT no caminho. A maioria dos VPS (Virtual Private Servidor) e servidores colocados são assim, embora alguns fornecedores bloqueiem Muitas portas de entrada por padrão.
Para esses servidores, tudo o que você precisa saber é o nome do host externo. O sistema O administrador irá dizer-lhe isso. O principal requisito é que este nome de host Pode ser pesquisado no DNS, e ele será mapeado para um endereço IPv4 ou IPv6 que Alcançará a máquina.
Se o seu nome de host for
example.net, então você criará o introdutor como esta::Tahoe create-introducer --hostname example.com ~ / introducer
Ou um servidor de armazenamento como ::
Tahoe create-node --hostname = example.net
Estes irão alocar uma porta TCP (por exemplo, 12345), atribuir
tub.portpara serTcp: 12345etub.locationserãotcp: example.com: 12345.Idealmente, isso também deveria funcionar para hosts compatíveis com IPv6 (onde o nome DNS Fornece um registro "AAAA", ou ambos "A" e "AAAA"). No entanto Tahoe-LAFS O suporte para IPv6 é novo e ainda pode ter problemas. Por favor, veja o ingresso
# 867_ para detalhes... _ # 867: https://tahoe-lafs.org/trac/tahoe-lafs/ticket/867
O servidor possui um endereço público IPv4 / IPv6
Se o host tiver um endereço IPv4 (público) rotativo (por exemplo,
203.0.113.1```), mas Nenhum nome DNS, você precisará escolher uma porta TCP (por exemplo,3457``) e usar o Segue::Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 3457
--porté uma "string de especificação de ponto de extremidade" que controla quais locais Porta em que o nó escuta.--locationé a "sugestão de conexão" que ele Anuncia para outros, e descreve as conexões de saída que essas Os clientes irão fazer, por isso precisa trabalhar a partir da sua localização na rede.Os nós Tahoe-LAFS escutam em todas as interfaces por padrão. Quando o host é Multi-homed, você pode querer fazer a ligação de escuta ligar apenas a uma Interface específica, adicionando uma opção
interface =ao--port =argumento::Tahoe create-node --port = tcp: 3457: interface = 203.0.113.1 - localização = tcp: 203.0.113.1: 3457
Se o endereço público do host for IPv6 em vez de IPv4, use colchetes para Envolva o endereço e altere o tipo de nó de extremidade para
tcp6::Tahoe create-node --port = tcp6: 3457 - localização = tcp: [2001: db8 :: 1]: 3457
Você pode usar
interface =para vincular a uma interface IPv6 específica também, no entanto Você deve fazer uma barra invertida - escapar dos dois pontos, porque, de outra forma, eles são interpretados Como delimitadores pelo idioma de especificação do "ponto final" torcido. o--location =argumento não precisa de dois pontos para serem escapados, porque eles são Envolto pelos colchetes ::Tahoe create-node --port = tcp6: 3457: interface = 2001 \: db8 \: \: 1 --location = tcp: [2001: db8 :: 1]: 3457
Para hosts somente IPv6 com registros DNS AAAA, se o simples
--hostname =A configuração não funciona, eles podem ser informados para ouvir especificamente Porta compatível com IPv6 com este ::Tahoe create-node --port = tcp6: 3457 - localização = tcp: example.net: 3457
O servidor está por trás de um firewall com encaminhamento de porta
Para configurar um nó de armazenamento por trás de um firewall com encaminhamento de porta, você irá precisa saber:
- Endereço IPv4 público do roteador
- A porta TCP que está disponível de fora da sua rede
- A porta TCP que é o destino de encaminhamento
- Endereço IPv4 interno do nó de armazenamento (o nó de armazenamento em si é
Desconhece esse endereço e não é usado durante
tahoe create-node, Mas o firewall deve ser configurado para enviar conexões para isso)
Os números de porta TCP internos e externos podem ser iguais ou diferentes Dependendo de como o encaminhamento da porta está configurado. Se é mapear portas 1-para-1, eo endereço IPv4 público do firewall é 203.0.113.1 (e Talvez o endereço IPv4 interno do nó de armazenamento seja 192.168.1.5), então Use um comando CLI como este ::
Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 3457
Se no entanto, o firewall / NAT-box encaminha a porta externa * 6656 * para o interno Porta 3457, então faça isso ::
Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 6656
Usando o I2P / Tor para evitar o encaminhamento da porta
Os serviços de cebola I2P e Tor, entre outras excelentes propriedades, também fornecem NAT Penetração sem encaminhamento de porta, nomes de host ou endereços IP. Então, configurando Um servidor que escuta apenas no Tor é simples ::
Tahoe create-node --listen = tor
Para mais informações sobre o uso de Tahoe-LAFS com I2p e Tor veja : Doc:
anonymity-configuration -
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28IPFS problems: Too much immutability
Content-addressing is unusable with an index or database that describes each piece of content. Since IPFS is fully content-addressable, nothing can be done with it unless you have a non-IPFS index or database, or an internal protocol for dynamic and updateable links.
The IPFS conceit made then go with the with the second option, which proved to be a failure. They even incentivized the creation of a database powered by IPFS, which couldn't be more misguided.
-
 @ 65038d69:1fff8852
2025-03-29 12:31:02
@ 65038d69:1fff8852
2025-03-29 12:31:02Minimum wage has been a hot topic as far back as I can remember. If you’re an employer it can feel like government needlessly meddling in the free market, while for employees it feels like its never high enough to make a difference. This is especially true where oversaturated labour markets are combined with high costs of living (HCOL) (which is pretty much everywhere at this point). Workers may need 2 or even 3 minimum wage jobs just to cover food, shelter, and transport in these areas, and would probably love to see minimum wage lifted. Employers in less-dense areas are faced with the opposite problem; even if they advertise pay “above minimum wage”, acquiring and keeping entry-level staff in HCOL areas is a constant battle. In this case, my recommendation is to localize your minimum wage.
In Canada most enforceable minimum wages are set by the provinces. Federal minimums apply to federal government employees (and some federally regulated industries). The problem with this is the sometimes broad disparities in cost of living (COL) between municipalities, especially between urban and rural. I’ve seen rent differences from 50% to 100% for comparable apartments. Applying the same minimum wage isn’t going to have the effect it’s meant to. If your staff can’t afford rent, they’re going to constantly be searching for something better, leading to high turnover. They’ll be forced into mercenary behaviours (see my previous post on “True Believers & Mercenaries”). Official minimum wages also lag behind inflation, but that’s a whole separate discussion (see my “What is Money?” series, starting with “Part 1 - What is Money?). On the flip-side, having a localized minimum wage allows your employees to stay settled where they are and gives them the freedom to be True Believers. You can work it directly into your job postings too; advertising wages that are based on local COL will have your inbox flooded with applications, allowing you to choose from the best instead of having to settle for the desperate. Let’s get into how to go about localizing your minimum wage.
First, look at a map and ponder how far most would be willing to commute to your workplace. Draw a rough circle with that as the radius. Everywhere inside this circle is fair game for everything to follow. Next, find some low-rent but livable apartments inside the circle and look up their rates. This will be your rent figure.
Transport is next. We’re going to use fuel cost as a “close enough” placeholder as actual costs will vary greatly between individuals. We’re also going to pick a “close enough” fuel efficiency for the same reason. I’ve chosen 8.5L/100KM, but you can adjust this. For example, full-size pickups may be more popular among your staff so that number may need to go up. Look up the average fuel prices for the last few months at retail stations within the circle, and the average working days per month for your staff. Now plug all of these numbers into the following formula and calculate. This will give you the monthly fuel cost: (fuel price x 8.5 x (circle radius KM x 2) / 100) x working days
Lastly, groceries. Like transport, we’re aiming for a “close enough” placeholder. You can substitute any items and volumes you like, but these are my recommendation to get an average monthly cost for an average minimum wage worker plus 1 dependant. Go to a generic grocery store within the circle and get the regular (non-sale) prices of the following: 3 x 3lb/1.36kg apples (averaged or middle price), 5 x single Long English cucumber, 1 x 10lb bag of potatoes, 2 x 4L 2% milk, 4 x 1 dozen large eggs, 2 x 600g block of cheese (average or middle price), 6 x loaf of brown or whole grain bakery bread (average or middle price), 5 x 1lb/454g lean ground beef, 1 x 4kg box frozen chicken breasts, and 1 x 3.5lb/1.6kg bag of jasmine rice.
Now that you have totals for the expenses, put those numbers into the following formula. This will give you total monthly living expenses: ((rent + groceries) / 0.45) + fuel Put that total into the following formula for the monthly paycheque total, pre-deductions. Insert current federal and provincial income tax rates for your jurisdiction: expenses / (1 - (provincial tax rate as decimal + federal tax rate as decimal + 0.05) With this final total you can divide by monthly working hours for an hourly wage, or multiply by 12 for an annual salary. I’ll provide an example of all of this at the bottom of the article.
After crunching these numbers you may have concluded that paying a localized minimum wage would eat into your profits. This may be the case initially, but lowering turnover rates and increasing the quality of your hires will save you money long-term. However, if it raises costs so high that the business would become unprofitable, you may need to consider that the business isn’t viable. Being dependant on employees willing to work for below the cost of living in your area will eventually end the business regardless, and I would argue is immoral.
Want help localizing your minimum wage? You can find us at scalebright.ca.
Sample localized minimum wage calculation: Rent: $1,200 Fuel cost: ((1.40 x 8.5 x (9.4 x 2) / 100) x 20 = $44.75 Groceries: $229.46 Apples: 23.97 Cucumbers: 14.95 Potatoes: 8.99 Milk: 11.90 Eggs: 17.40 Cheese: 20.58 Bread: 23.94 Ground beef: 42.45 Chicken breasts: 49.99 Rice: 15.29 Total expenses: ((1200 + 229.46) / 0.45) + 44.75 = $3,221.33 Total monthly paycheque: 3221.33 / (1 - (0.10 + 0.15 + 0.05) = $4,601.90 Hourly: 4601.90 / 160 = $28.76 Annual salary: 4601.90 x 12 = $55,222.80 -
 @ 65038d69:1fff8852
2025-03-29 12:31:02
@ 65038d69:1fff8852
2025-03-29 12:31:02“What is money?” sounds like a bit of a silly question. You’d probably hold up some cash or maybe flash your debit card. But I challenge you with this: imagine a 5-year-old asking you this question. How would you answer? If you showed them a $20 bill, they might respond with, “I know that’s a money, but what is it?” If you manage to explain that the bill is worth $20, they’re next question is going to be, “how many is your card?” How would you answer that? At some point you’d probably end up trying to distract them with something else while you worked to ignore the dread feeling that you should have those answers, but don’t. Never fear, for we will attempt to explain it in such a way that you’ll have an answer for 5, 15, 50, or 95-year-olds by the time we’re done this 4-part series!
Let’s start with an overview of the history of money. I highly recommend further reading on each of these; we’re going to skim most of them today. In the beginning, there was simple barter. If we each had something the other wanted, we could trade. But if the scale of what we want to trade is lopsided, say, chickens for a cow, or cows for a house, how do you make the trade work? Or what if you wanted to save up for a larger purchase? The answer is a placeholder; something that represents value in trade. An early example of this is the rai stones in Micronesia, which are essentially carved rocks. These worked well for store of value and medium of exchange, but not so much for unit of account. Precious metal coins arose later, with the most common being gold, silver, copper, and bronze. These worked well for all three of the major elements.
Store of value, medium of exchange, and unit of account are the three major elements of any system of money. Store of value means it holds its value well over time. If you put a gold coin in a box in your house and retrieve it 10 years later, it’s still a gold coin and should be in the same physical condition as it was when stored. Medium of exchange means it’s widely accepted for trade. This one is a bit trickier, but if you’re the Roman Empire you can simply make everyone accept denarius. Unit of account means units should hold the same value everywhere they’re used. This is similarly tricky, but if you’re the Dutch East India Company you can simply make VOC-stamped coins global denominations.
Renaissance-era Italy is where modern banking was born. A key concept invented during this time was the double-entry ledger, or double-entry bookkeeping system. In short, every transaction is recorded, and every transaction has two entries: one with an amount leaving an account, and one with the same amount going into a different account. At the end of every block of time all accounts will have an aggregate balance of 0, with individual accounts either having a credit or debit. This system is still in use today, as well as the broad use of credit notes in place of coins or direct trade. Credit notes could be written against an account and given in trade, and later the receiver could take the note to the bank, who would then record the transaction as complete. If this sounds familiar, that’s because modern cheques are the same thing.
Modern money systems take these concepts a step further. Banks now maintain a whole network of double-entry ledgers and in most countries banks are no longer required to hold reserves matching their credit notes issued. Credit notes are also the total physical currency, also known as a fiat currency, or currency by authority or decree. This essentially means fiat money has no intrinsic value other than the promise of the issuing authority to treat it as valid and the willingness of others to accept it in trade. For an example of “willingness to accept in trade”, many retail stores in Canada will accept American dollars even though they’re not required to.
If you’re now thinking, “thanks for the history lesson, but what does this mean to me and the payment terminal in my store?”, the answer will come 2 weeks from now when we cover the Canadian dollar. In the meantime if you want to learn a bit more about the systems our modern money is based on, read up on the Roman Empire and their currency, as well as that of the Dutch East India Company. If you really want to dive deep, Renaissance Italy’s banking systems are also fascinating and a little closer to us on the timeline.
-
 @ fd06f542:8d6d54cd
2025-04-15 02:38:14
@ fd06f542:8d6d54cd
2025-04-15 02:38:14排名随机, 列表正在增加中。
Cody Tseng
jumble.social 的作者
https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
- Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
- Building 👨💻:
- https://github.com/CodyTseng/jumble
- https://github.com/CodyTseng/nostr-relay-tray
- https://github.com/CodyTseng/danmakustr
- https://github.com/CodyTseng/nostr-relay-nestjs
- https://github.com/CodyTseng/nostr-relay
- https://github.com/CodyTseng
阿甘
- @agan0
- 0xchat.com
- canidae40@coinos.io
- https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce
joomaen
- Follows you
- joomaen.com
-
95aebd@wallet.yakihonne.com
-
nobot
- https://joomaen.filegear-sg.me/
- https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0
颜值精选官
- wasp@ok0.org
- 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好!
- https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz
6svjszwk
- 6svjszwk@ok0.org
- 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi
-
low-time-preference
-
anarcho-capitalism
-
libertarianism
-
bitcoin #monero
- https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk
𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳
- everyday@iris.to
- 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。
- 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。
- 黑暗森林时代,当好小透明。
- bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww
- https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke
nostr_cn_dev
npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash
Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 * https://www.duozhutuan.com nostrhttp demo * https://github.com/duozhutuan/NostrBridge * * https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm *
CXPLAY
- lightning@cxplay.org
- 😉很高兴遇到你, 你可以叫我 CX 或 CXPLAY, 这个名字没有特殊含义, 无需在意.
- ©本账号下所有内容如未经特殊声明均使用 CC BY-NC-SA 4.0 许可协议授权.
- 🌐如果您在 Fediverse 收到本账号的内容则说明您的实例已与 Mostr.pub 或 Momostr.pink Bridge 互联, 您所看到的账号为镜像, 所有账号内容正在跨网传递. 如有必要请检查原始页面.
- 🧑💻正在提供中文本地化(i10n): #Amethyst #Amber #Citrine #Soapbox #Ditto #Alby
- https://cx.ms/
https://jumble.social/users/npub1gd8e0xfkylc7v8c5a6hkpj4gelwwcy99jt90lqjseqjj2t253s2s6ch58h
w
- 0xchat的作者
- 0xchat@getalby.com
- Building for 0xchat
- https://www.0xchat.com/
- https://jumble.social/users/npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl
Michael
- highman@blink.sv
- Composer Artist | Musician
- 🎹🎼🎤🏸🏝️🐕❤️
- 在這裡可以看到「我看世界」的樣子
- 他是光良
- https://jumble.social/users/npub1kr5vqlelt8l47s2z0l47z4myqg897m04vrnaqks3emwryca3al7sv83ry3
-
 @ d36a437b:4480d6a5
2023-08-04 10:33:07
@ d36a437b:4480d6a5
2023-08-04 10:33:07导论 在康德哲学中我们的行动不仅仅是受到感官经验和外部因素的驱动,还涉及到我们内在的理性和意志。自由意志使我们能够根据道德原则和理性的指导来选择和行动,而不是被感官欲望或外在条件所束缚。
康德指出,自由意志并不意味着完全自由地做出任何选择。他认为自由意志有其限制和约束,需要在道德律法的指引下行动。自由意志的真正价值在于我们能够根据道德原则做出自主的决策和行动,而不是纯粹地追求个人欲望或外在利益。
康德的自由意志观念与他对伦理学和道德认识的理解密切相关。他认为,自由意志是个体道德责任的基础,我们的行动应该根据普遍适用的道德原则来决策,并为我们的行为负责。
然而海德格尔认为,康德将自由意志与知识的能力相混淆。康德认为自由行为是基于理性和智力的决策,但海德格尔指出,知识只是对现实世界的表面了解,并不能真正理解人类存在的本质和自由的实质;他认为,人的存在受到生活环境、社会文化背景以及语言等因素的影响和塑造,这些都限制了个体的选择和决策。海德格尔认为,真正的自由意志应该考虑到人的存在和具体境遇,而不仅仅停留在理性和决策的层面。
Part i 权力与自由意志
综上所述,完全无底线且不理性的自由早在康德就被批判了并且被认为是错误的理念
言论自由可以被视为康德自由意志的一个重要应用领域。言论自由是指个体表达思想、意见和信仰的权利,不受政府或其他机构的干预或压制。这个权利是公民社会和民主制度的基石,也是知识交流和进步的关键。
康德的自由意志观点强调个体的独立性和自主性,以及对道德准则的遵循。言论自由可以被视为个体运用自由意志的一种方式,通过言辞表达自己的思想和见解。言论自由使个体能够参与公共讨论和辩论,促进知识的共享和社会的进步。 自由意志应当在道德行为中的限制。自由不是放任任意行为的纵容,而是在理性和普遍准则的指引下进行选择。
言论自由使个体能够独立思考、形成独立的意见,并表达这些意见而不受外部干预或压制。言论自由为个体提供了一个平台,在其中展示他们的自主性和独立思考的能力,也是人权的基本体现,也是人之所以为人而不是被硬件(肉体)与软件(思想)所限制的“机器”
Part ii 马克思主义中的言论自由
很明显,卡尔马克思相较于康德和海德格尔对自由这一词汇的观点更加的全面
根据马克思的历史辩证法,上一个时代的真理必然在下一个时代所呈现,马克思对于自由意志,言论自由的看法与康德完全不同
马克思主义的角度来看,个体的自由意志受到社会、经济和阶级关系的制约。个体的行为和意识是在特定历史时期和社会环境下形成的。然而,在特定条件下,个体仍然具有一定的选择权和自主性,可以通过集体行动来争取自身权益和解放。
从阶级利益意识形态去分析,马克思主义认为在资本主义社会中,社会中存在阶级斗争,并且不同阶级拥有不同的阶级利益,统治阶级(资产阶级)掌握了经济和政治权力,并通过控制媒体、教育等手段来塑造和宣传符合其利益的意识形态。因此,言论自由在资本主义社会中常常受到限制,被用于服务统治阶级的利益。
从思想压迫与言论管控角度来说,资本主义社会存在着对劳动者的压迫和剥削。这种压迫不仅体现在经济方面,还包括思想和意识形态上的控制。统治阶级通过掌控话语权和言论管制,限制了被压迫阶级对自己状况的认识和声音的表达。言论自由的受限导致被压迫阶级难以真实地表达自己的需求和反抗。
从解放与革命来说,言论自由是解放与革命的一大工具,是被压迫阶级争取解放的重要工具之一;通过言论自由,被压迫阶级能够表达自己的不满、观点和组织起来参与革命运动。
马克思主义认为,建立共产主义社会后,将会有一个无产阶级专政的阶段。在这个阶段,对统治阶级的反抗将受到限制,以确保无产阶级的权力稳定。然而,马克思认为,在这种情况下,言论自由仍然可以存在,并且将为广大群众提供更多发声和参与决策的机会,所以自由并非与资本主义统治相绑定
结论
不论是以阶级,经济,社会还是哲学,我们都得出了一个结论,就是无产者,人民,社会,世界需要言论自由,并且是理性,以道德为准则的言论自由,这是一个理想的社会样态
自由不是以私有财产为权力代表的权力关系,也不是以私有财产为原则组建的社会,家庭。而是以伦理道德为底线自由原则与人权
以资产阶级法权为基础支撑的国家不过是资产阶级商议内部事务的委员会罢,与工人没有任何干系
致谢
作者:Bill Charles 感谢DAOrayaki对本文章的创作支持
-
 @ 147ac18e:ef1ca1ba
2025-04-13 01:57:13
@ 147ac18e:ef1ca1ba
2025-04-13 01:57:13In a recent episode of The Survival Podcast, host Jack Spirko presents a contrarian view on the current trade war and tariffs imposed by the U.S. government. Far from being a chaotic or irrational policy, Jack argues that these tariffs are part of a broader strategic plan to rewire the global trade system in America's favor—and to force long-overdue changes in the domestic economy. Here's a breakdown of the core reasons Jack believes this is happening (or will happen) as a result of the tariffs:In a recent episode of The Survival Podcast, host Jack Spirko presents a contrarian view on the current trade war and tariffs imposed by the U.S. government. Far from being a chaotic or irrational policy, Jack argues that these tariffs are part of a broader strategic plan to rewire the global trade system in America's favor—and to force long-overdue changes in the domestic economy. Here's a breakdown of the core reasons Jack believes this is happening (or will happen) as a result of the tariffs:
1. Tariffs Are a Tool, Not the Goal
Jack’s central thesis is that tariffs are not meant to be a permanent fixture—they’re a pressure tactic. The goal isn’t protectionism for its own sake, but rather to reset trade relationships that have historically disadvantaged the U.S. For example, Taiwan responded to the tariffs not with retaliation but by proactively offering to reduce barriers and increase imports from the U.S. That, Jack says, is the intended outcome: cooperation on better terms.
2. Forced Deleveraging to Prevent Collapse
One of the boldest claims Jack makes is that the Trump administration used the tariffs as a catalyst to trigger a “controlled burn” of an over-leveraged stock market. According to him, large institutions were deeply leveraged in equities, and had the bubble popped organically later in the year, it would have required massive bailouts. Instead, the shock caused by tariffs triggered early deleveraging, avoiding systemic failure.
“I’m telling you, a bailout scenario was just avoided... This was intentional.” – Jack Spirko
3. Global Re-shoring and Domestic Manufacturing
Tariffs are incentivizing companies to move production back to the U.S., especially in key areas like semiconductors, energy, and industrial goods. This shift is being further accelerated by global geopolitical instability, creating a “once-in-a-generation” opportunity to rebuild small-town America and domestic supply chains.
4. Not Inflationary—Strategically Deflationary
Jack challenges conventional economic wisdom by arguing that tariffs themselves do not cause inflation, because inflation is a function of monetary expansion—not rising prices alone. In fact, he believes this economic shift may lead to deflation in some sectors, particularly as companies liquidate inventory, lower prices to remain competitive, and reduce reliance on foreign supply chains.
“Rising prices alone are not inflation. Inflation is expansion of the money supply.” – Jack Spirko
5. Energy Costs Will Fall
A drop in global oil prices, partially due to reduced transport needs as manufacturing reshoring increases, plays into the strategy. Jack notes that oil at $60 per barrel weakens adversaries like Russia (whose economy depends heavily on high oil prices) while keeping U.S. production viable. Lower energy costs also benefit domestic manufacturers.
6. The Digital Dollar & Global Dollarization
Alongside this industrial shift, the U.S. is poised to roll out a “digital dollar” infrastructure, giving global access to stablecoins backed by U.S. banks. Jack frames this as an effort to further entrench the dollar as the world’s dominant currency—ensuring continued global demand and export leverage without the need for perpetual military enforcement.
7. A Window of Opportunity for Americans
For individuals, Jack sees this economic transformation as a rare chance to accumulate long-term assets—stocks, Bitcoin, and real estate—while prices are suppressed. He warns that those who panic and sell are operating with a “poverty mindset,” whereas those who stay the course will benefit from what he describes as “the greatest fire sale of productive assets in a generation.”
Conclusion: Not a Collapse, But a Reset
Rather than viewing tariffs as a harbinger of economic doom, Jack presents them as part of a forced evolution—an uncomfortable but necessary reboot of the U.S. economic operating system. Whether or not it works as intended, he argues, this is not a haphazard policy. It’s a calculated reshaping of global and domestic economic dynamics, and one with enormous implications for trade, energy, inflation, and the average American investor.
-
 @ 65038d69:1fff8852
2025-03-29 12:28:24
@ 65038d69:1fff8852
2025-03-29 12:28:24We’ve all been in meetings that seem to be stuck in an unending loop of “discussions” going nowhere while simultaneously ratcheting up everyone’s emotions as the minutes past dinner continue to climb. You stand to leave as you reach your limit and declare, “It’s past my bedtime”. If only there was a way to make meetings more efficient!
The gold standard for meeting organization is “Robert’s Rules of Order”, the original having been published in 1876 and currently in it’s 12th edition (https://robertsrules.com). It’s quite the tome at over 800 pages, which makes sense given that it’s meant to be a complete procedural guide. If that feels like overkill for your 5-person weekly department check-in, there’s an “In Brief” edition available meant for just such cases. Our focus today will be less procedural and more on the squishy human side.
People are social creatures who generally prefer friendly conversation over stiff formalities. This will be your primary hurdle as left unstructured most meetings will migrate from handling business to visiting. My first recommendation is to intentionally schedule social time before and after the meeting. You may have seen this communicated as “doors open” and “doors close” times on event announcements. Or you can break the fourth wall and label it “social time”. Either way, explain its purpose to your attendees and make it clear that its optional. Most will appreciate having it; these meetings may be the only time they see each other, but for some its just business and they won’t want to feel pressured into awkward conversation.
Intentional social time is best paired with my next tip: begin the formal portion exactly at the advertised start time. This will encourage everyone to arrive on time (or ideally early), and might allow you to finish early. (Who doesn’t like that‽) If your attendees are used to a loose start time it might seem jarring at first, but if you break the fourth wall (again) and explain why you’re doing it, you shouldn’t have many arguments. If you have late arrivals, don’t interrupt the flow or pause to catch them up. Its their responsibility to arrive on time, and failing that its their responsibility to catch themselves up. Again, it won’t take long to normalize a hard start time. I also recommend advertising and sticking to a hard stop time as well. The nice thing about a stop time is that its only definite in one direction; you don’t have to stick to it if you’re done early. It’s primary purpose is to reassure everyone that the meeting won’t get drug out. Evening meeting attendees with young children at home will be especially grateful.
If this is starting to feel like a lot of details to keep track of, fear not, for there is a solution invented long ago: the formal meeting agenda! I’ve included a basic template below, but an internet search will provide a cornucopia of formats and options. My rule of thumb is the longer the meeting, the further in advance you should provide an agenda. As a starting point I aim for a week / 5 business days for any longer than an hour. You’ll also want to include any written reports and statements. This will be another item you may get some pushback on; many will be used to delivering verbal reports with very little prep. Written versions have several advantages (see my previous posts on the importance of writing things down, especially “Writing Things Down Is For Boys Too”), including giving attendees a chance to review and absorb the information before the meeting, keeping the reports concise, and making inclusion in the minutes much easier. I also like to include statements on old and new business items, which takes us into the next, and possibly most controversial, item.
Alongside social visiting, one of the biggest time-eaters in meetings is “discussion”. In my opinion (here comes the controversial part), meetings shouldn’t have discussions, only decisions and formalizations. All discussion should happen before the meeting. For example, let's say a new piece of equipment needs to be purchased, and an official vote is needed to do so. The next business meeting is not the place to discuss this. Options, pros and cons, bids or quotes, and most importantly, opinions and emotions surrounding the decision, should be hashed out and aired between stakeholders in an informal fashion on their own time. Billy and Sally don’t need to have a shouting match about the colour options while everyone else awkwardly stares at their shoes in the middle of the weekly stand-up. They can have their cat fight in the privacy of the HR office or at the local Timmies. I make a bit of an exception for what I call “statements”, though with tight controls. If Billy acquiesces to Sally’s demands to buy the blue model instead of the yellow one but still wants his oppositions known, he might be tempted to unleash a rant if, during the meeting, the chairperson says something like, “Anyone have any thoughts on this equipment purchase?” Chances of this happening are high for business items surrounded by high emotions, such as layoffs or budget cuts. This is where the statement can be a powerful tool to give everyone most of what they want. Have those who wish to create brief written statements. Your pitch to them is that it can be included in the agenda with all the other important business, everyone will see it (even those who can’t make it to the meeting), there’s no chance of their opinion being misrepresented, and it can easily be included in the minutes. You can optionally allow them to read their statement aloud during the meeting, but keep tight control on this. Again, emotions may be running high, and someone hearing their nemesis vocalize an opinion they disagree with may be enough to set them off. Make it clear that the statement will be read for the record, and no responses or discussion will follow, as discussion has already happened.
I’ve mentioned the chairperson a few times. This person should be, without question, in control. They should have absolute dictatorial power over the meeting, and importantly, over who has permission to speak. Anyone who disagrees with this power can be asked to leave. It sounds harsh, but a meeting without a human “talking stick” will fall to those without the social awareness to refrain from interrupting, or those willing to be the loudest. Have the chairperson wield their omnipotence for the good of the people.
Need help with planning or executing your meetings? You can find us at scalebright.ca.
``` Example Meeting Agenda: Meeting Title Organization / Team / Group Name Meeting Date, Start Time, and Stop Time Meeting Location Chairperson Participants / Invitees
Order of Business: Call to Order / Start Approval of previous minutes Approval of reports Old business New business Adjournment
Appendices: A: Previous Minutes B: Report 1 C: Statement from John Doe on Business Item 1 D: Quote for Business Item 2 ```
-
 @ 7e538978:a5987ab6
2025-04-10 13:14:04
@ 7e538978:a5987ab6
2025-04-10 13:14:04After five years and over 6,000 commits, LNbits has reached a momentous milestone: Version 1.0.0 is here. LNbits is officially out of beta!
This release represents the five years relentless development, dedication, bug-hunting, feature-building, and community involvement. What started as a lightweight Lightning wallet application for Lightning Network payments has evolved into one of the most versatile, modular, and widely-used Bitcoin tools in the space.
We want to offer a heartfelt thank you to every contributor, developer, tester, and user—from those running LNbits for personal use to the communities and businesses who rely on it every day. Your feedback, bug reports, feature requests, and support have made LNbits what it is today.
🚀 Key Highlights in v1.0.0
- LNbits now at v1.0.0 – the software is stable, hardened, and production-ready.
- Vue 3 migration – a complete frontend overhaul for performance and long-term maintainability.
- WebSocket payments – faster and more efficient, replacing older SSE and long-polling methods.
- New lnbits.sh install script – simplifies setup and local deployment.
- Access Control Lists (ACL) – token-based permissions for powerful role and scope control.
- Admin tools:
- Admin payments overview
- Toggle outgoing payments
- View payments from deleted wallets
- NWC (Nostr Wallet Connect) support
- Login with Nostr or OAuth – expanding integration and authentication options
💱 Fiat & Exchange Upgrades
- Custom exchange providers
- Improved fiat precision
- Wallet-level fiat tracking and labels
- Support for Bitpay and Yadio fiat rate providers
🧑🎨 UI / UX Improvements New Login/Register interface
- Default theme for new users
- Custom background images
- Visual refresh with new themes (including neon and light/dark modes)
- Revamped Pay Invoice dialog and invoice creation
- Custom wallet icons/colours
- CSV export and in-wallet payment filtering
🛠️ Developer Tools & Internal Enhancements Migration to pyjwt, updated to breez-sdk 0.6.6, pyln-client 24.5
- Support for Python 3.10–3.13
- New nodemanager for managing Lightning channels
- Backend refactors, improved database handling, type hinting, and extension logic
- More robust testing and CI support
🩹 Maintenance & Fixes Persistent fix for admin removal bug
- Improved extension handling
- Bug fixes across wallet logic, funding sources, and legacy compatibility
- Dozens of improvements to reliability, performance, and developer experience
🎉 A Huge Thank You
To every developer, translator, tester, UX contributor, node runner, and user: thank you.
LNbits wouldn’t be what it is without your involvement. Whether you've written code, opened issues, translated labels, or simply used it and given feedback—this release is yours too.
Here's to the next chapter!
-
 @ 65038d69:1fff8852
2025-03-29 12:24:26
@ 65038d69:1fff8852
2025-03-29 12:24:26“Technology never changes” sounds insane, doesn’t it? Of course it changes! Far too fast! New models of smartphones, laptops, refrigerators, cars, and toasters every year! And that’s just hardware; software and the internet move even faster. Every time you open your social media app of choice you’re greeted with a new thing to figure out. But under the hood of version 999 of all these newfangled widgets, they’re all the same as they’ve ever been, because technology never changes.
Does that still sound crazy to you? Excellent! That means I have you hooked for the rest of this article! All humour aside, when I say, “technology never changes”, I’m talking about the underlying concepts, how we use technology, and on the organization side, how we plan for it. That last one will be our focus today. The tech strategies I help organizations implement haven’t changed since I started in tech, and my predecessors would probably mirror the same, especially since they’re the ones I learned these concepts from.
Let’s dive in. If you’ve been involved in vehicle fleet management this first one will be familiar. For technology hardware there’s a concept called an “evergreen program”, which is essentially a schedule of when hardware is cycled or replaced. End-user hardware such as laptops, desktops, and smartphones is 3 years, servers is 6, wired network elements are 9, and wireless (mostly access points) is 6. These numbers aren’t written in stone or the same for every org; they’re just meant to be a starting point. But here's the big secret: most of this equipment, if it’s business-grade, properly maintained, and treated well, will last at least 10 years. The reason for the comparatively short evergreen cycles is two-fold: downtime can be more expensive than replacing equipment, and replacing equipment is usually a tough sell and put off as long as possible regardless of programs or policy. That’s an article all by itself; lets move along for now. Those evergreen program and lifetime numbers haven’t changed. Sure there’s a new Macbook every year and your cousin’s buddy who makes 7 figures working for a California design firm gets them on release day, but those are the exception. Your 5-person non-profit is going to replace laptops on double cycles based on tech strategy that hasn’t changed. Because technology never changes.
I mentioned software earlier and that it moves even faster. While this is true, tech strategy around it hasn’t changed. I’ll use the ubiquitous Microsoft Windows and Microsoft Office suite as examples. New major versions used to release roughly every 3 years. If you’re replacing your laptops and desktops on a 3 year cycle, you never really have to worry about upgrading Windows or Office separately. Today Microsoft has migrated most of their products to a subscription model, but the cycle is the same. Because technology never changes.
But what about AI? Isn’t it quadrupling in power every few minutes? Hasn’t it used the energy of a thousand suns to drink the oceans dry in order to feed it’s insatiable quantum-powered hunger for knowledge and control? No, it hasn’t. In fact, if news articles are to be believed; ChatGPT et al. have run up against a bit of a wall. My prediction is that we’ll start seeing AI in more common usage sometime late this year, which, not-so-coincidentally, will be about 3 years since it’s public release. Because technology never changes.
-
 @ 65038d69:1fff8852
2025-03-29 12:19:19
@ 65038d69:1fff8852
2025-03-29 12:19:19Look at any white-collar office job posting from the last few decades and you’re likely to see something like “basic computers skills” listed as a requirement. “Great,” you think to yourself, “I can use technology, after all, I managed to find this job posting!” And if you’re on the hiring end for a position that’ll be spending six to eight hours in front of screen, you’d certainly hope applicants would know that they need to be able to use a computer. Ten years of bookkeeping experience? Reception? Managing remote staff? In a Venn diagram of work experience and basic computer skills, those should be a near complete overlap! We shouldn’t need to train them at all! Can we be sure though? It turns out “basic computer skills” doesn’t have a universally accepted definition.
Since basic computer skills doesn’t have an official definition we can point to, lets attempt to create one ourselves. I argue for reading comprehension as the base skill underlying all the others we’re going to talk about (see “One Skill To Rule Them All” for more on this). Unfortunately reading comprehension doesn’t have a universal measurement either. I used to use “6th grade reading level” as my go-to, but today’s media is full of articles on changing standards and outcomes in public education, so that’s no longer dependable. If you’re interviewing someone, try providing them with a copy of the job posting and asking them questions about it that require some simple inference. For a more advanced option, I’ve included a test you can administer that covers reading comprehension and several other elements.
How about typing? Should basic computer skills include home row typing ability? What about speed requirements? If we’re talking about basic skills, I’d say no to both of those. While “chicken pecking” with two fingers probably wouldn’t qualify you for a staff writing position at a newspaper, I consider formal typing (especially with a speed requirement) to be an intermediate skill. So your applicant should be able to navigate a keyboard without assistance, but that’s all.
Email is probably the most universal computer task of the modern era. I’ve included it in the test template. Users should be able to recognize an email address and the “To”, “Subject”, and “Body” fields in an email client, even an unfamiliar one. Email interfaces have kept their same basic elements since the 90s.
The most controversial skill I’ve seen talked about lately is the ability to navigate and use a file system. The advent of smartphones and tablets, and the ubiquity of Chromebooks in schools, has led to new workers who have never had to save a file to a “documents” folder, or infer that a photo could most likely be found in a “pictures” folder. The strongest counterargument I’ve read is that between “recent” lists and search functions we shouldn’t need to know how to navigate file structures. I disagree, so I’ve included this skill in the test as well.
Lastly, safety and security. What’s considered “basic” varies wildly. Could you recognize a phishing email pretending to be from your boss? What about the difference between an ad link and a regular result in an internet search? I haven’t included this in the test as needs and policies are different at every workplace, but it’s a good idea to consider it when planning your interviews and internal training. An employee who clicks the links in every suspicious email without a second thought is a security disaster waiting to happen.
Here’s the skills test I promised. There are two ways of administering it; either provide the interviewee with a computer to use, or use screenshots and have them verbally walk you through the steps they would take. The latter requires a bit more visual and verbal knowledge transference and self-awareness so I only recommend it if providing a company computer isn’t a possibility. You’ll also need to customize it; for example YOURTEXTEDITOR needs to be replaced with whatever program is standard for your org, i.e. Microsoft Word.
Instructions for the Applicant: Please read the instructions below carefully and perform the steps described. After completing the task, answer the follow-up questions about the process. Task: 1. Open YOURTEXTEDITOR on the computer. 2. Create a new file and write the following without the quotes: “Welcome to the team! Your onboarding kit is on your desk.” 3. Save the file with the name "Team Message - " ending with today’s date, in the "FOLDERORSHAREDRIVE" folder. 4. Format the text to bold and change the font size to 14. 5. Close the application. 6. Open YOUREMAILCLIENT. 7. Send an email to INTERVIEWER with the subject “Team Message”. In the email, let them know that the file is ready. 8. Attach the file and send the email. Instructions for the Interviewers: After they’ve completed the task, ask the following questions about the process. Interviewees should be allowed to keep their instructions in front of them, but DO NOT tell them they can refer to them unless they ask. 1. What was the name of the first program you opened? 2. If you couldn’t save the file to the “FOLDERORSHAREDRIVE” folder/share drive, where would you have saved it? Why? 3. Who did you send the email to? 4. What did you name the file? 5. What changes, if any, would you make to the instructions? Post-interview analysis: The following is reasoning for the instructions and questions, and what to look for in the interviewee’s actions and responses. Task: 1. They should be able to find an application on the computer with little assistance. 2. They should be able to type the sentence into the document and understand the instructions to leave out the quotation marks. Observe their typing style (home row vs single finger presses) and speed. 3. Ability to remember or find today’s date and to save a document to a specific location. 4. Ability to format text. 5. They should remember to save the document or answer the automated prompt to save the document. 6. Same as question 1, but with a different application. 7. They should be able to send an email with an attachment. Ideally they’ll either know, or be able to figure out, how to look up the interviewer in the company address book. Also, the ability to write without being told explicitly what to say. 8. The ability to locate and attach a file to an email. Follow-up questions: 0. Allowing them access to the instructions without explicitly telling them they can refer to them will test their sense of agency. Asking permission is fine as some will feel the follow-up questions are a test, and most people are used to tests or exams being closed-book. It will also test their ability to find the information they need within the task instructions. 1. Ability to recall or locate the information. 2. Ability and sense of agency to make a best-option decision when faced with adversity. 3. Ability to recall or locate the information. 4. Ability to recall or locate the information. 5. Tests self-awareness around needs or preferences for directions. “None” is also an acceptable answer if they had no struggles with any of the task steps.Share this article with anyone working on job postings or interviews in your organization, and please feel free to use the skills test content in any way you like. It’s best modified for your specific needs!
Need someone to assist with skills assessment, training, or hiring processes? You can find us at scalebright.ca.
-
 @ 3b3a42d3:d192e325
2025-04-10 08:57:51
@ 3b3a42d3:d192e325
2025-04-10 08:57:51Atomic Signature Swaps (ASS) over Nostr is a protocol for atomically exchanging Schnorr signatures using Nostr events for orchestration. This new primitive enables multiple interesting applications like:
- Getting paid to publish specific Nostr events
- Issuing automatic payment receipts
- Contract signing in exchange for payment
- P2P asset exchanges
- Trading and enforcement of asset option contracts
- Payment in exchange for Nostr-based credentials or access tokens
- Exchanging GMs 🌞
It only requires that (i) the involved signatures be Schnorr signatures using the secp256k1 curve and that (ii) at least one of those signatures be accessible to both parties. These requirements are naturally met by Nostr events (published to relays), Taproot transactions (published to the mempool and later to the blockchain), and Cashu payments (using mints that support NUT-07, allowing any pair of these signatures to be swapped atomically.
How the Cryptographic Magic Works 🪄
This is a Schnorr signature
(Zₓ, s):s = z + H(Zₓ || P || m)⋅kIf you haven't seen it before, don't worry, neither did I until three weeks ago.
The signature scalar s is the the value a signer with private key
k(and public keyP = k⋅G) must calculate to prove his commitment over the messagemgiven a randomly generated noncez(Zₓis just the x-coordinate of the public pointZ = z⋅G).His a hash function (sha256 with the tag "BIP0340/challenge" when dealing with BIP340),||just means to concatenate andGis the generator point of the elliptic curve, used to derive public values from private ones.Now that you understand what this equation means, let's just rename
z = r + t. We can do that,zis just a randomly generated number that can be represented as the sum of two other numbers. It also follows thatz⋅G = r⋅G + t⋅G ⇔ Z = R + T. Putting it all back into the definition of a Schnorr signature we get:s = (r + t) + H((R + T)ₓ || P || m)⋅kWhich is the same as:
s = sₐ + twheresₐ = r + H((R + T)ₓ || P || m)⋅ksₐis what we call the adaptor signature scalar) and t is the secret.((R + T)ₓ, sₐ)is an incomplete signature that just becomes valid by add the secret t to thesₐ:s = sₐ + tWhat is also important for our purposes is that by getting access to the valid signature s, one can also extract t from it by just subtracting
sₐ:t = s - sₐThe specific value of
tdepends on our choice of the public pointT, sinceRis just a public point derived from a randomly generated noncer.So how do we choose
Tso that it requires the secret t to be the signature over a specific messagem'by an specific public keyP'? (without knowing the value oft)Let's start with the definition of t as a valid Schnorr signature by P' over m':
t = r' + H(R'ₓ || P' || m')⋅k' ⇔ t⋅G = r'⋅G + H(R'ₓ || P' || m')⋅k'⋅GThat is the same as:
T = R' + H(R'ₓ || P' || m')⋅P'Notice that in order to calculate the appropriate
Tthat requirestto be an specific signature scalar, we only need to know the public nonceR'used to generate that signature.In summary: in order to atomically swap Schnorr signatures, one party
P'must provide a public nonceR', while the other partyPmust provide an adaptor signature using that nonce:sₐ = r + H((R + T)ₓ || P || m)⋅kwhereT = R' + H(R'ₓ || P' || m')⋅P'P'(the nonce provider) can then add his own signature t to the adaptor signaturesₐin order to get a valid signature byP, i.e.s = sₐ + t. When he publishes this signature (as a Nostr event, Cashu transaction or Taproot transaction), it becomes accessible toPthat can now extract the signaturetbyP'and also make use of it.Important considerations
A signature may not be useful at the end of the swap if it unlocks funds that have already been spent, or that are vulnerable to fee bidding wars.
When a swap involves a Taproot UTXO, it must always use a 2-of-2 multisig timelock to avoid those issues.
Cashu tokens do not require this measure when its signature is revealed first, because the mint won't reveal the other signature if they can't be successfully claimed, but they also require a 2-of-2 multisig timelock when its signature is only revealed last (what is unavoidable in cashu for cashu swaps).
For Nostr events, whoever receives the signature first needs to publish it to at least one relay that is accessible by the other party. This is a reasonable expectation in most cases, but may be an issue if the event kind involved is meant to be used privately.
How to Orchestrate the Swap over Nostr?
Before going into the specific event kinds, it is important to recognize what are the requirements they must meet and what are the concerns they must address. There are mainly three requirements:
- Both parties must agree on the messages they are going to sign
- One party must provide a public nonce
- The other party must provide an adaptor signature using that nonce
There is also a fundamental asymmetry in the roles of both parties, resulting in the following significant downsides for the party that generates the adaptor signature:
- NIP-07 and remote signers do not currently support the generation of adaptor signatures, so he must either insert his nsec in the client or use a fork of another signer
- There is an overhead of retrieving the completed signature containing the secret, either from the blockchain, mint endpoint or finding the appropriate relay
- There is risk he may not get his side of the deal if the other party only uses his signature privately, as I have already mentioned
- There is risk of losing funds by not extracting or using the signature before its timelock expires. The other party has no risk since his own signature won't be exposed by just not using the signature he received.
The protocol must meet all those requirements, allowing for some kind of role negotiation and while trying to reduce the necessary hops needed to complete the swap.
Swap Proposal Event (kind:455)
This event enables a proposer and his counterparty to agree on the specific messages whose signatures they intend to exchange. The
contentfield is the following stringified JSON:{ "give": <signature spec (required)>, "take": <signature spec (required)>, "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>", "description": "<Info about the proposal (optional)>", "nonce": "<Signature public nonce (optional)>", "enc_s": "<Encrypted signature scalar (optional)>" }The field
roleindicates what the proposer will provide during the swap, either the nonce or the adaptor. When this optional field is not provided, the counterparty may decide whether he will send a nonce back in a Swap Nonce event or a Swap Adaptor event using thenonce(optionally) provided by in the Swap Proposal in order to avoid one hop of interaction.The
enc_sfield may be used to store the encrypted scalar of the signature associated with thenonce, since this information is necessary later when completing the adaptor signature received from the other party.A
signature specspecifies thetypeand all necessary information for producing and verifying a given signature. In the case of signatures for Nostr events, it contain a template with all the fields, exceptpubkey,idandsig:{ "type": "nostr", "template": { "kind": "<kind>" "content": "<content>" "tags": [ … ], "created_at": "<created_at>" } }In the case of Cashu payments, a simplified
signature specjust needs to specify the payment amount and an array of mints trusted by the proposer:{ "type": "cashu", "amount": "<amount>", "mint": ["<acceptable mint_url>", …] }This works when the payer provides the adaptor signature, but it still needs to be extended to also work when the payer is the one receiving the adaptor signature. In the later case, the
signature specmust also include atimelockand the derived public keysYof each Cashu Proof, but for now let's just ignore this situation. It should be mentioned that the mint must be trusted by both parties and also support Token state check (NUT-07) for revealing the completed adaptor signature and P2PK spending conditions (NUT-11) for the cryptographic scheme to work.The
tagsare:"p", the proposal counterparty's public key (required)"a", akind:30455Swap Listing event or an application specific version of it (optional)
Forget about this Swap Listing event for now, I will get to it later...
Swap Nonce Event (kind:456) - Optional
This is an optional event for the Swap Proposal receiver to provide the public nonce of his signature when the proposal does not include a nonce or when he does not want to provide the adaptor signature due to the downsides previously mentioned. The
contentfield is the following stringified JSON:{ "nonce": "<Signature public nonce>", "enc_s": "<Encrypted signature scalar (optional)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Swap Adaptor Event (kind:457)
The
contentfield is the following stringified JSON:{ "adaptors": [ { "sa": "<Adaptor signature scalar>", "R": "<Signer's public nonce (including parity byte)>", "T": "<Adaptor point (including parity byte)>", "Y": "<Cashu proof derived public key (if applicable)>", }, …], "cashu": "<Cashu V4 token (if applicable)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Discoverability
The Swap Listing event previously mentioned as an optional tag in the Swap Proposal may be used to find an appropriate counterparty for a swap. It allows a user to announce what he wants to accomplish, what his requirements are and what is still open for negotiation.
Swap Listing Event (kind:30455)
The
contentfield is the following stringified JSON:{ "description": "<Information about the listing (required)>", "give": <partial signature spec (optional)>, "take": <partial signature spec (optional)>, "examples: [<take signature spec>], // optional "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>" }The
descriptionfield describes the restrictions on counterparties and signatures the user is willing to accept.A
partial signature specis an incompletesignature specused in Swap Proposal eventskind:455where omitting fields signals that they are still open for negotiation.The
examplesfield is an array ofsignature specsthe user would be willing totake.The
tagsare:"d", a unique listing id (required)"s", the status of the listingdraft | open | closed(required)"t", topics related to this listing (optional)"p", public keys to notify about the proposal (optional)
Application Specific Swap Listings
Since Swap Listings are still fairly generic, it is expected that specific use cases define new event kinds based on the generic listing. Those application specific swap listing would be easier to filter by clients and may impose restrictions and add new fields and/or tags. The following are some examples under development:
Sponsored Events
This listing is designed for users looking to promote content on the Nostr network, as well as for those who want to monetize their accounts by sharing curated sponsored content with their existing audiences.
It follows the same format as the generic Swap Listing event, but uses the
kind:30456instead.The following new tags are included:
"k", event kind being sponsored (required)"title", campaign title (optional)
It is required that at least one
signature spec(giveand/ortake) must have"type": "nostr"and also contain the following tag["sponsor", "<pubkey>", "<attestation>"]with the sponsor's public key and his signature over the signature spec without the sponsor tag as his attestation. This last requirement enables clients to disclose and/or filter sponsored events.Asset Swaps
This listing is designed for users looking for counterparties to swap different assets that can be transferred using Schnorr signatures, like any unit of Cashu tokens, Bitcoin or other asset IOUs issued using Taproot.
It follows the same format as the generic Swap Listing event, but uses the
kind:30457instead.It requires the following additional tags:
"t", asset pair to be swapped (e.g."btcusd")"t", asset being offered (e.g."btc")"t", accepted payment method (e.g."cashu","taproot")
Swap Negotiation
From finding an appropriate Swap Listing to publishing a Swap Proposal, there may be some kind of negotiation between the involved parties, e.g. agreeing on the amount to be paid by one of the parties or the exact content of a Nostr event signed by the other party. There are many ways to accomplish that and clients may implement it as they see fit for their specific goals. Some suggestions are:
- Adding
kind:1111Comments to the Swap Listing or an existing Swap Proposal - Exchanging tentative Swap Proposals back and forth until an agreement is reached
- Simple exchanges of DMs
- Out of band communication (e.g. Signal)
Work to be done
I've been refining this specification as I develop some proof-of-concept clients to experience its flaws and trade-offs in practice. I left the signature spec for Taproot signatures out of the current document as I still have to experiment with it. I will probably find some important orchestration issues related to dealing with
2-of-2 multisig timelocks, which also affects Cashu transactions when spent last, that may require further adjustments to what was presented here.The main goal of this article is to find other people interested in this concept and willing to provide valuable feedback before a PR is opened in the NIPs repository for broader discussions.
References
- GM Swap- Nostr client for atomically exchanging GM notes. Live demo available here.
- Sig4Sats Script - A Typescript script demonstrating the swap of a Cashu payment for a signed Nostr event.
- Loudr- Nostr client under development for sponsoring the publication of Nostr events. Live demo available at loudr.me.
- Poelstra, A. (2017). Scriptless Scripts. Blockstream Research. https://github.com/BlockstreamResearch/scriptless-scripts
-
 @ 65038d69:1fff8852
2025-03-29 12:10:15
@ 65038d69:1fff8852
2025-03-29 12:10:15“Can you help make our website good?” is one of the most loaded questions I get. There are many aspects to this question’s galactic gravitas, and their root is another question: what makes a website good?
Before we get there, we have a few other questions that need answering. The first is whether you actually need a website. Would a social media presence and a Google Maps listing do the same job? Or do you need a dedicated online shop or some other functionality that a Facebook Page can’t provide? Who’s your target market? Is it people who don’t have social media accounts or wouldn’t want to mix their social media presence with your business?
Let’s say you’ve gone through all of that and decided you do indeed need a website. What makes a website “good” can be divided into two aspects: engineering and design. In the context of websites, engineering is the behind the scenes stuff that makes it go (think of the mechanical bits of a car), and design is how it looks and feels (all the stuff you see and touch in a car). Unfortunately for us, most places these overlap they’re also juxtaposed. To see this in action head over to simple.scalebright.ca. You’ll notice that it loads extremely quickly and works well on screens of any size. This site was built with an “engineering first” mindset. Designers generally loath this kind of website. Not because it loads fast or scales well, but because to do those things I had to sacrifice design. There are no graphics or images, one font, and only four total colours in use (if you count black and white). There are no fancy contact forms, loading animations, white space considerations, borders, boxes, or bulbous billowing bedazzlements. Just cold, ruthless efficiency. I love it! But it’s not necessarily good.
This takes us into the next consideration. A good website doesn’t necessarily appeal to you; it’s supposed to appeal to your target audience. You might not be your target audience. If you are, great! That’ll make figuring out what your target audience wants in a website easier. Either way, be sure to have some chats with them and keep what they say in mind.
Okay, I know I just finished saying that the highly simplified version of my website isn’t good, but I want to warn you away from the opposite: over-design and over-engineering. Over-design usually manifests as visual overload; too many colours, too many graphics or photos, too much motion. Over-engineering is too much mechanical complexity; a one-page professional bio site doesn’t need to run on a dedicated server on WordPress with fifteen plugins.
There isn’t going to be a one-size-fits-all answer to “what makes a website good?”, because no two website are going to be identical. You’ll probably end up engaging a professional website design firm to both help answer that question for your specific scenario, and to build it for you. Here are some of the questions they’re going to ask and some hints for answering them.
What are your colours, fonts, logos, and other visual assets? If you don’t have these the firm should be able to help (usually for an extra fee), though smaller firms may need to subcontract the work out.
What are the core functions of your website? Is it an online store? Professional bio? Hospitality booking site? A link hub or landing page?
Do you have your website copy ready to go? “Copy” in this context refers to the text that will go on your website. Slogans, product and service descriptions, staff bios, and anything else that consists of a collection of words. If you don’t have your copy, you’ll either need to prepare to write it yourself or hire a third party to write it for you. It’s been my experience that website design firms are very strict about not writing copy, and generally won’t subcontract it either.
Do you have a preferred CMS? A CMS is a content management system, which is a fancy way of saying “thing that makes your website easier to add content to”. WordPress, Joomla, and Drupal are CMSs. Squarespace, GoDaddy, and Wix could be considered CMSs for our purposes too. 99% of you probably don’t care, and that’s a perfectly acceptable answer to give your firm.
What’s your budget? While most of us would probably prefer to spend zero, groceries continue to cost money, so none of us work for free. As of the writing of this article, a multi-page website built by a design firm will range between $10,000 and $30,000.
Want someone to “just take care of” all this website shenanigans for you? You can find us at scalebright.ca.
-
 @ f7f4e308:b44d67f4
2025-04-09 02:12:18
@ f7f4e308:b44d67f4
2025-04-09 02:12:18https://sns-video-hw.xhscdn.com/stream/1/110/258/01e7ec7be81a85850103700195f3c4ba45_258.mp4
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 68c90cf3:99458f5c
2025-04-04 16:06:10
@ 68c90cf3:99458f5c
2025-04-04 16:06:10I have two Nostr profiles I use for different subject matter, and I wanted a way to manage and track zaps for each. Using Alby Hub I created two isolated Lightning wallets each associated with one of the profile’s nsecs.
YakiHonne made it easy to connect the associated wallets with the profiles. The user interface is well designed to show balances for each.
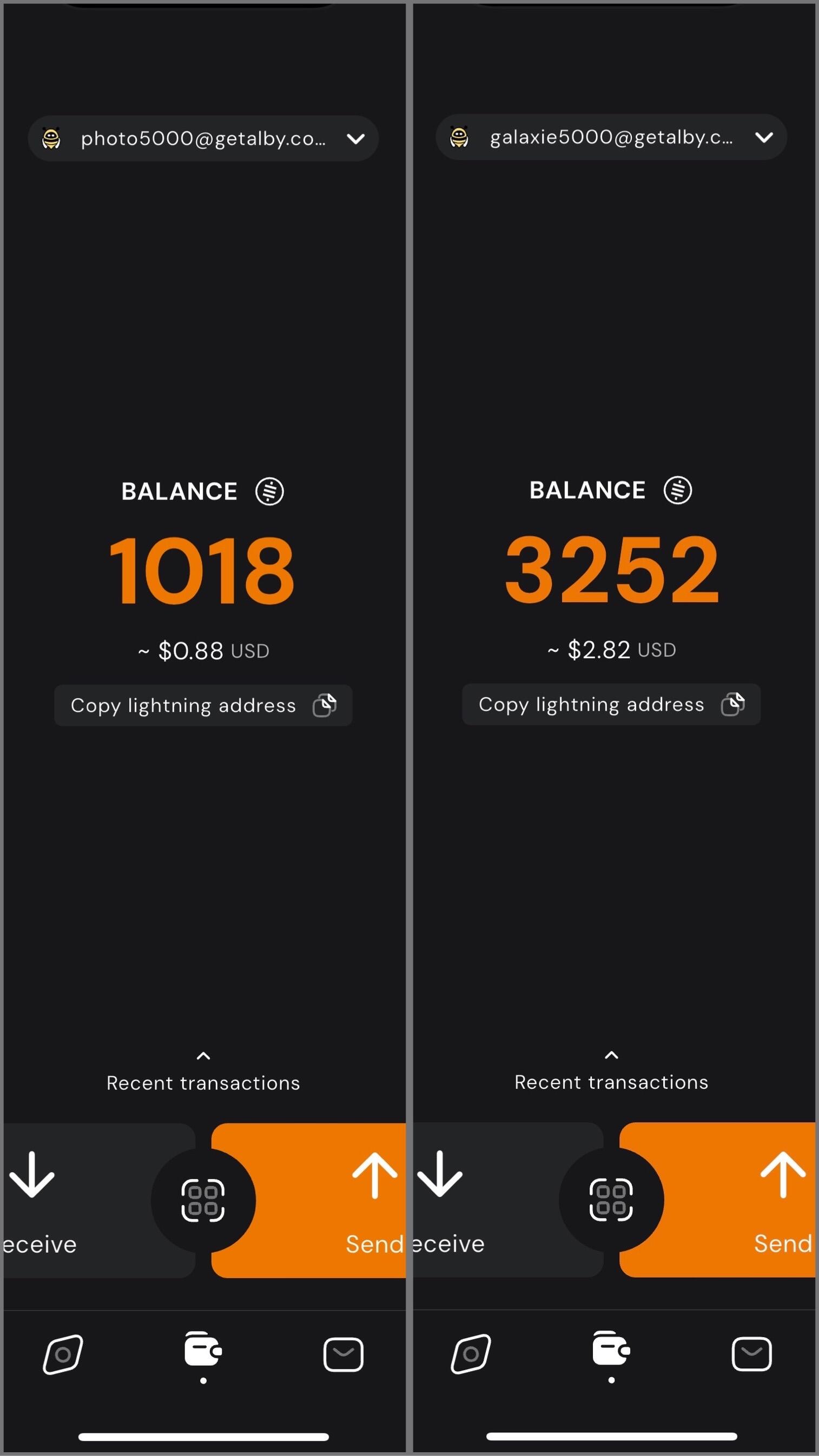
In my case, I have one profile for photography related content, and the other for Bitcoin, Nostr, and technology related content. I can easily switch between the two, sending and receiving zaps on each while staying up to date on balances and viewing transactions.
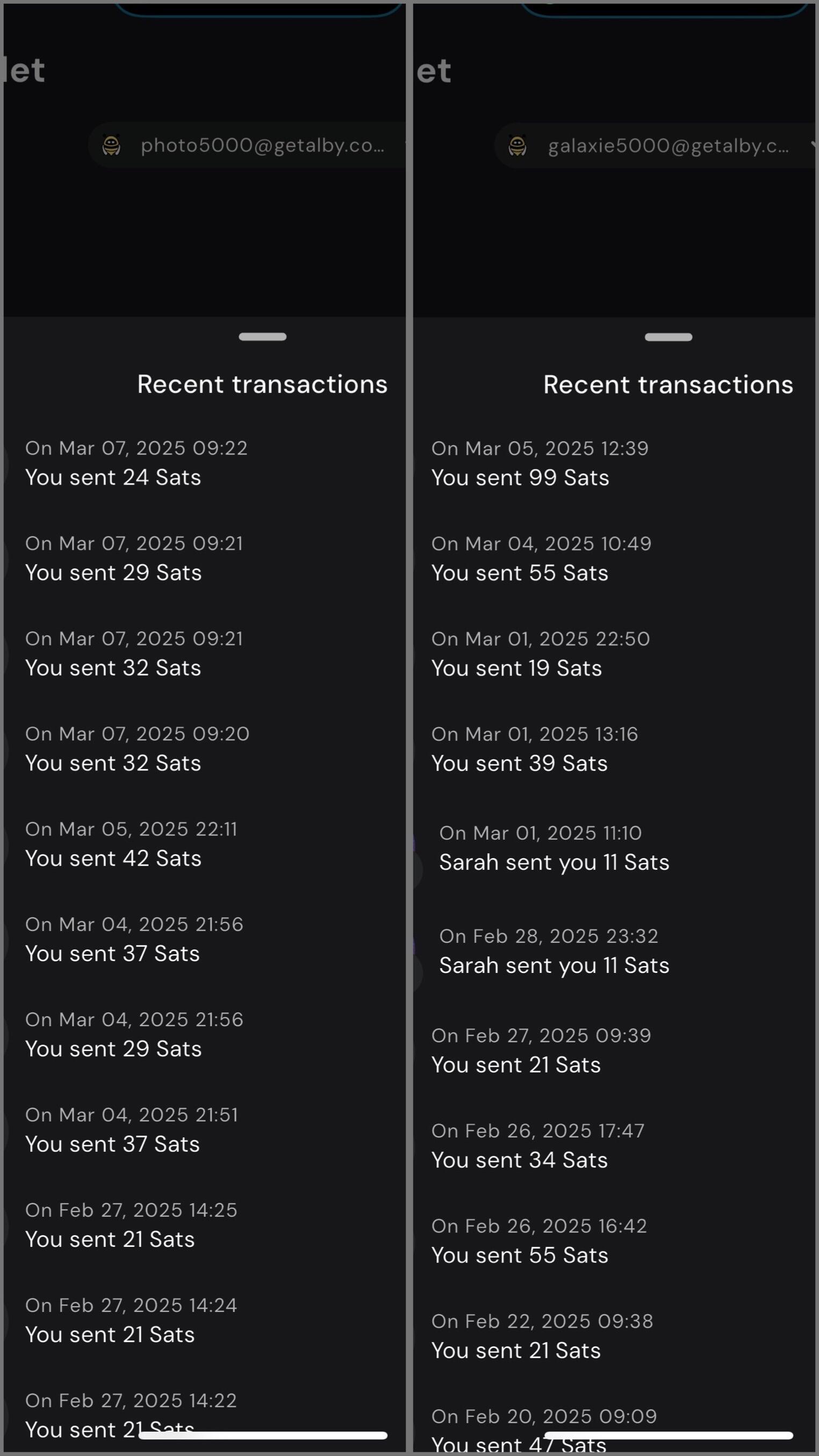
Using my self-hosted Alby Hub I can manage Lightning channels and wallets while sending and receiving zaps for multiple profiles with YakiHonne.
YakiHonne #AlbyHub #Lightning #Bitcoin #Nostr
-
 @ 65038d69:1fff8852
2025-03-29 12:07:06
@ 65038d69:1fff8852
2025-03-29 12:07:06I’ve been on the internet since the mid 90s. Once I started “cyber-schooling” a few years later my time spent in front of a screen skyrocketed. One of the time vortices both for and outside of school was finding things on the internet. Everything from encyclopedia-style information pieces to news articles to music to games; the hunt was relentless.
Search engines were the primary was this was done. In the early days my school officially recommended Ask Jeeves, but the students found Google’s results much more thorough. Us little scientists-in-training were even running parallel searches, recording outcomes, and sharing results. We eventually got in trouble for wrongthink...I mean...not following instructions, but were vindicated soon after when the school's recommendations changed to "use whatever search engine you like, as long as the results chosen are quality sources".
The problem of “how to find things on the internet” has recently returned. “Google it” is no longer the genericized verb it once was. Grand tomes and PHD theses have been written on the subject of why, but most point to motives and monetization. The original problem was finding things, and the solution was search. But how would the bills get paid? Computers are expensive! Printing newspapers is expensive too, and the solution was the same for both: sell advertising space. Unfortunately for us users, that has become the primary business for much of the internet. Search engines are no longer motivated to get you the results you’re looking for as quickly as possible, but to keep you on their platform looking at ads. Pundits have coined the term “enshittification” (which even has it’s own Wikipedia page now) to describe the phenomenon.
Worry not, for not all is lost! There are still ways to find things on the internet. Methods vary depending on what kind of things you’re looking for. One of my most common searches is for how to do things; everything from home repairs to mechanical to technology. My primary method for this is to use Google to search Reddit. Reddit is a massive collection of forums with almost two decades of human-generated content. Unfortunately it’s built-in search is mostly terrible, so that’s where Google comes in. Do the same Google search you’d normally do (say, “how to fix a squeaky door”), but add “site:reddit.com” to the end. This tells Google to only show results from Reddit. What you’ll get is forum threads and comments from (mostly) real humans with real human experiences. Of course humans and their commentary can still be deeply flawed, so stay skeptical of what you read, but it’s largely a much better experience than a naked Google search.
Less mainstream search engines are trying their hands at paid subscriptions as a way to avoid the advertising hell-spiral. Kagi is one I’ve been trying, though admittedly not as often as I should. They do have a free tier if you want to sample it.
A more high-tech solution is AI systems. ChatGPT recently released a tool specifically for internet searches, though their general prompt tool has been usable for this for a while. Kagi also has an AI-powered search tier. Both are pretty expensive for casual users though.
Another recommendation is to frequent interest or topic-specific forums and blogs. If you find yourself regularly needing vehicle repair tips, try joining a forum on the subject. Same goes for most other do-it-yourself tasks. You may even make some internet friends! Blogs are also a great way to find things and get connected to experts (shameless plug fully intended).
Lastly, some interesting things are happening on the Nostr protocol that could help bring information together without the commercial overreach. (See “Become Unbannable” for more on Nostr.) I’ve been using a site called Zap Cooking (https://zap.cooking) to browse recipes. Recipes here are Nostr notes (posts) that have been formatted and categorized, and can be commented on, rated, and tipped, all using the free and open Nostr protocol. No algorithms, no banks, no governments, and no ads!
Want help with or training on finding things on the internet? You can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-29 12:03:23
@ 65038d69:1fff8852
2025-03-29 12:03:23“Sam did it!” You can hear the edge in the child’s voice as they attempt to shift blame for whatever minor misdeed they may-or-may-not have masterminded. In the court of humanity our feelings take wide precedence over objective justice. Even if there’s no fallout or formal punishment for that thing we did wrong, we really don’t like taking the blame.
Personal responsibility isn’t only about taking blame for the negative. As we’ll define it for the purposes of this article, it means taking ownership of decisions you make and the actions you take based on them. By extension you will also be taking ownership of the outcomes, both the successes and failures. Your mind is probably already imagining all sorts of scenarios this could apply to both at work and at home, but our focus will be mostly in the workplace.
Imagine working in a utopia where everyone perfectly executes personal responsibility. You would never have to worry about someone blaming you for the failure of their project, because it’s their project. You would know in advance that if your project is a success you’ll get 100% of the accolades, because it’s your project. With these two things alone, wouldn’t you feel a new level of motivation to give it your all? To take risks and innovate? You would have a new level of trust in your coworkers too. There would be no motive for micromanagement, for doing so would mean taking someone else’s responsibility upon yourself. Morale and productivity would skyrocket!
You can easily imagine the opposite as well; you may have thought of your own workplace in a negative light as soon as you read the title and clicked the link. Unfortunately in I.T. (being a panoptic presence in most organizations) we’re an easy target. “I can’t work, my computer’s broken, and I.T. hasn’t fixed it yet! They’re so slow, am-I-right?” “The file deleted itself; stupid computers!” “It’s not my fault that we didn’t deliver on time; the printer’s broken and it’s not my job to fix it!” sigh Enough gloom, let’s move on to how to make personal responsibility great again!
It's a simple concept; remind yourself that our decisions are ours, our actions are ours, and the results are ours. No exceptions. I’ll give you an example. When my wife and I are travelling somewhere it’s usually up to me to decide where to eat. I’m usually driving, and I’m also the head of our household, so it’s my decision. My decision, my actions, and most importantly, my results to own. If I choose a place and my wife doesn’t like the ambiance or menu or amount of cheese they put on everything, that’s on me. The weight can be heavy and feel unjust. But it isn’t unjust. It’s perfectly, objectively just. It’s my decision, my actions, and my results to own. There are upsides for both of us; I am now further motivated to pick someplace I know she’ll like and she gets to play “Passenger Princess”, and I get to bathe in the social bragging rights of being crowned “King of the Husbands” for being intuitive and attentive enough to know what she’d like and get it for her. It’s timeless and primordial: “Oh husband, you hunted and brought back a mammoth! I love mammoth steak! You are brave and strong and clearly the greatest of all husbands!” Her words would eco through our cave commune and all would look to us for hot tips to share on their relationship blog cave paintings.
You might still be thinking of your workplace and your coworkers who seem to want to blame you for everything that goes wrong. What can you do to get them on the personal responsibility train? The only way to do it is to lead by example. The moment you try to tell them or make them they’ll see it as an attack and blame you, which is exactly the problem you’re trying to avoid! You can’t suggest it, hint at it, or leave an anonymous note. You can’t have someone else talk to them about it or send this article and say, “I read this and thought it was interesting and thought you would think it’s interesting too.” This only way to teach others about personal responsibility is to show them. Which makes me writing this massively ironic. I take full responsibility for this!
My last tip is to make sure to celebrate the wins, both yours and other’s! This is especially true for others you’re trying to influence. Remember the accolades we imagined getting earlier and how much that would motivate you? That’s what you’re trying to instill in others. Positive reinforcement is much stronger than negative, so hand your praises out like candy!
Want to go against my recommendations and bring me into your workplace to talk about personal responsibility? You can find us at scalebright.ca.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28idea: Hosted-channels Lightning wallet that runs in the browser
Communicates over HTTP with a server that is actually connected to the Lightning Network, but generates preimages and onions locally, doing everything like the Hosted Channels protocol says. Just the communication method changes.
Could use this library: https://www.npmjs.com/package/bolt04
-
 @ a005da43:e6bf3b09
2024-08-21 19:56:24
@ a005da43:e6bf3b09
2024-08-21 19:56:24fdsafdsafdsafdsa
originally posted at https://stacker.news/items/459392
-
 @ 65038d69:1fff8852
2025-03-29 12:00:27
@ 65038d69:1fff8852
2025-03-29 12:00:27The Americans just had a big election, and Canada’s next has been effectively underway for a while now. Automated moderation systems are being increasingly relied upon by large social media networks and are running amok with bans (I may be biased on this one, see “The Technology Deleted Me”). Opinions are everywhere, and many social media users live in fear of getting booted from their platform of choice over an innocuous post. “Of choice” usually being where the largest concentration of their connections also have accounts. For me that’s Facebook; for others it might be Instagram, Snapchat, Bluesky, or X.
What if there was a social media network built in such a way that you couldn’t be banned? Where your posts couldn’t be removed? Where you couldn’t be “put in the corner” by a group admin who didn’t like that the recipe page you shared had the word “crap” in it? Wouldn’t that be great? Yes, this does mean extreme (or straight-up illegal) content could be posted, but that’s happening on mainstream social media as well. Monitoring and banning isn’t working there so there’s no reason to repeat it elsewhere.
The unbannable social media I’m bringing to you today is called “Nostr”; "Notes and Other Stuff Transmitted by Relays”. How it works is explained in the name; notes (posts) are transmitted from a client (app on your device) to relays (servers) which are then transmitted to other relays and clients connected to them. I’ll explain in more detail as we go through the setup process.
Step 1: Pick a client. I like Damus on iOS and noStrudel on desktop. Nostur is also popular on iOS. Amethyst and Primal are popular on Android. Pick the one you most like the look of.
Step 2: Set up an “account”. On Nostr you won’t have an account in the traditional sense. You’ll instead have a public/private key set (also known as a keypair). Think of your public key as your username and your private key as your password; only you won’t need to pick, memorize, or regularly use either of them. Your client will do most of that for you. Install the app of your choosing, launch it, and you’ll be walked through the account creation process. I strongly recommend copying your public key (the long random string that starts with “npub”) and your private key (the long random string that starts with “nsec”) to a password manager (see “Ugh, Passwords!” for more on password managers).
Optional: Step 2.5: Set up your “NIP-05 identifier”. This is totally optional, and can be done later if you aren’t up for it right now. A NIP-05 identifier looks identical to an email address (
name@domain.something) and is used as an easier way for others to find your profile. There are several free and paid services for this, most of which come with other benefits and services. A popular free one is Nostrcheck.me.Step 3: Choose some relays. Most clients will have a pre-configured set of public relays that work fine for most users. If you think of yourself as just a normal person trying to not be banned, you can skip this step. For everyone else, reach out to me for recommendations. A whole ‘nother article could be written on the subject of relays for niche needs.
Step 4: Find friends to follow. You can start with me if you like, by searching for my public key (
npub1kw893e70hve5ymc8kxr75d8m9wcuaaasqzn37xvea6l4f39q04fs7zusa4), or my NIP-05 (tnperron@nostr.theorangepillapp.com).Optional: Step 5: Post something! Also totally optional, but highly recommended! Even a simple “Hello, world!” will let others visiting your profile know that your account is being actively used.
That’s it, you’re now unbannable! How, you ask? There are two keys to this (pun fully intended). The first is that your public/private keypair is yours to control, can be loaded into any client, and used to connect to any relay (though you may need to pay for access to some). The second is that if someone operating a relay decides they don’t want to relay your posts anymore, you can still use any other on the big wide internet. You can even run your own relay if you want! No one can stop you!
Want help with any of these steps, or more details on advanced options like running your own node? You can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-29 11:50:52
@ 65038d69:1fff8852
2025-03-29 11:50:52The internet has had tutorials for job applications for a while; I remember searching for and reviewing them as part of “Career and Life Management (CALM)” in grade school. But it still never hurts to go back to the basics!
Applications fall into two categories; what I’ll call “human-read” and “machine-read”. Machine-read applications are specifically designed for automated recruitment systems. These systems tend to require specific layouts and formatting, as well as focus on keywords and academic degrees (even if the job doesn’t require them). They don’t read very well for humans though. I’d also argue that you probably don’t want to work for an employer who uses such systems, but that’s a separate topic. Human-read applications are as the name suggests; applications designed for human review. Those are the type we’re going to focus on today.
Our goals with our application are going to be to maximize the chances the receiver (usually a receptionist, HR staff, or recruiter) will pass along our application to the decision maker (usually HR staff or interview panel member) who will shortlist you for an interview, and to convey all the relevant information to the interview panel before your interview. We’re going to do this by creating a cover letter and resume combo that is unique, but also follows a professional format.
Let’s start with the page template we’re going to use for both documents. Start with a blank page. In the header in the upper left corner, list your name, email, and town & province. Make your name 5 to 8 font sizes larger than the rest, and bold if the font needs more pop. In the upper right corner, write yourself a short byline that would make a Madison Avenue advertising executive proud. Workshop it with your friends or family, but don’t worry about spending too much time on it. Mine says “Process management, Results through consistent and conscientious excellence”. The idea is to have your audience say to themselves, “ooo, that sounds professional”, then move on. Make the first line the same font size as your name. Next, add a splash of colour or some basic shapes as a background to the header. Pick a maximum of two colours and a minimalist geometric design. Make sure it’s simple; if it’s too busy it’ll look like a primary school art project. Again, you want your audience say to themselves, “ooo, that looks professional”, then move on. Now go to the first line in the body of the document and type “title”, then go to the third line and type “body”. Make the title font the same size as your name in the header, and change it to the primary colour of your header background. Finally, save two separate copies of this file; one labelled “your name resume” and the other labelled “your name cover letter”.
Congratulations, the design part is over! If you’re like me, that was the hard part. On to the content! Open the cover letter document. Change the title text to “To:”. Go to the body line and paste in the following. For the listeners, you can find the text to be copied in the written version of this post on our website.
``` Receiver name Receiver email Receiver title Receiver organization Receiver city, province
Submission date
Greeting, Paragraph 1: Brief personal introduction and job being applied for. Paragraph 2: Brief professional introduction, framed as how you would be a good fit for the organization. Paragraph 3: Extended professional introduction, framed as how you be a good fit for this specific job. Paragraph 4: Three to four questions you would have for the interview panel if you were chosen to be interviewed. Paragraph 5: Follow-up and interview availability. Sign-off and signature. ```
Congratulations, you now have your own personalized cover letter template! Simply replace the placeholder and instruction text with the real thing. Five paragraphs may seem like a lot, but if you’re sufficiently brief (as you should be), the whole thing should fit on a single page. If it spills over, rework the paragraph text until it does. Turning to a second page has an ethereal effect that will make your cover letter feel like “too much”. It’s purely emotional and subconscious, but it’s real and to be avoided if you want to make a good first impression, which is your cover letter’s primary purpose!
Save and close, and open the resume. Center the title on the page and change the text to “Executive Summary”. Move to the body and paste the following. Again, for the listeners, you can find the text to be copied in the written version on our website.
``` First highlighted skill category or character trait paragraph. Two to three sentences. Second highlighted skill category or character trait paragraph. Two to three sentences. Third highlighted skill category or character trait paragraph. Two to three sentences. Bulleted list of three to six specific soft skills.
Centered title: Professional or Work Experience (choose one) Employer - City, Province - years worked (i.e. 2015-2020 or 2022-current) Job title Two to three item bulleted list summarizing duties. Can be written long form, but be brief. (copy this as many times as needed)
Centered title: Education, Certifications, & Training (remove words that don’t apply to you) Title Certifying or training body name, City, Province (copy this as many times as needed)
Centered title: Proficiencies Bulleted list of five to ten specific hard skills. Do not repeat from soft skills above.
Centered title: Volunteer & Civic Affiliations (if you have none, use Hobbies) Bulleted list, no more than six items. ```
Same as the cover letter, replace the placeholder and instruction text with the real thing. The whole resume should fit on two pages. If it spills over, the first thing you can reduce is the number of work experience sections. You don’t need to include your entire work history, but it is best to not leave gaps if you can. We’re at the final step. The home stretch. You can do it! I believe in you! We’re going to export both documents as PDFs, then print copies, and inspect for errors or issues. “Why the PDFs and printing?” you ask? PDFs are the universal document format (see my previous post on the subject, “What is a PDF?”), and the interview panel will most likely want to print copies for themselves for the interview. Printing a copy for yourself will allow to you make sure everything looks good on paper as well as on a screen. You’re going to take your copy with, as well as a printed copy of the job posting, to use as a reference during your interview. No matter how well you think you know the material, it’s always good to have a reference. Physically referencing these documents during the interview will also help you look prepared and factual. What sounds better, “I thought the job posting said 40 hours per week?...”, or “here, in the second paragraph, the job posting says 40 hours per week”?
Want help with your job application? Or assistance with interviewing potential employees? You can find us as scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 14:20:35
@ 65038d69:1fff8852
2025-03-28 14:20:35What is “the cloud”? And more importantly, who cares? The term has been in use for years and is long past the point of being a buzzword, but it might become relevant again as we enter the next phase of the cycle.
The cloud (as we’ll define it) is any computer system, in part or in full, that runs in someone else’s facility. Facebook is in the cloud. Etsy is in the cloud. Your bank’s internal systems are probably not in the cloud; they run their systems “on-prem” (short for on-premises, or in their own facilities) for regulatory and security reasons.
But if on-prem is more secure, why would we use the cloud at all? Its mostly convenience and scaling. If you want a website its much easier to set up a Squarespace or GoDaddy account and use their building tools than it is to get an enterprise internet connection, buy a server, install and set up all the software needed, and make the website from scratch. Maintenance is also much easier. Ask any QuickBooks user about the convenience of QuickBooks Online vs Desktop. Also if your needs change, cloud providers will happily automatically bill you more for the increased usage, as apposed to needing to buy more or upgrade your equipment to handle the load.
If the cloud is so much easier, why use on-prem at all? And what was that you said about cycles? Accounting and human resources. (Not HR as in the department, but the actual human resources available to you.) In accounting, the cloud is considered a service and falls under OpEx (operating expenses), while on-prem equipment such as servers fall under CapEx (capital expenses). And eeeeeveryone has a different, and often very strong, opinion on which is better. On costs, they’re pretty similar if averaged over 5, 10, or 20+ years, but with on-prem the CapEx is mostly up-front, so that can scare people over to the easy monthly payments of the cloud. On-prem also usually requires access to more technical human resources. If you’re a small organization you probably don’t have dedicated I.T. staff or maybe even the budget to hire contractors. All of this leads to cycles between the cloud and on-prem being more popular.
That all sounds like a sales pitch for cloud, but I have a sales pitch for you for on-prem. And that sales pitch is sovereignty. What happens to your records if QuickBooks closes your account? Your social media presence if Facebook does the same? How will you access your money if your bank freezes your accounts? These types of hazards can be mitigated by using on-prem instead of the cloud. It gives you far more control over your data and services. You can also build your own “private cloud” if you want to, maintaining control but making your systems available away from your office or home.
Want to get ahead of the cycle and move some of your systems on-prem? You can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 14:20:35
@ 65038d69:1fff8852
2025-03-28 14:20:35Last week our household acquired a dog. I’ve had and trained dogs before; four in total over the course of about 20 years. But it’s been about 6 years without one, and this one is an inside dog, which is completely new to me. Old habits die hard though and I’m finding nuggets of skills and knowledge slowly returning.
I was lucky enough to get some formal training in dog training in my early teens, and I remember noticing some of the base training methods we used with dogs matched the human learning methods our family talked about. When I later joined the workforce this idea was reinforced during onboardings and later when I was asked to train others on technology platforms. People and dogs learn best with repetition, reward (also known as positive reinforcement), and a combination of learning styles.
You’ve probably heard of the classic learning styles framed one way or another depending on the book, workshop, or TED Talk you experienced that one time. The three core styles of auditory, visual, and kinesthetic overlap in training people and dogs. (I feel the need to pause and reiterate that while I am comparing people to dogs, I’m not conflating the two. You are not a dog. I might be, because on the internet nobody knows you’re a dog, but I’m not calling you one.) For people, auditory may be a professor lecturing or a friend explaining a new board game. For dogs, verbal commands such as “Fido, sit!” fill that role. Visual for people could be a diagram or demonstration, while for dogs a hand signal does the same. Kinesthetic is a bit different; for people we sometimes call it “hands on” or the 4H motto of “learn to do by doing”, while for dogs it might be physically placing them a sitting position while giving the sit command.
Combining the styles is the best way to achieve maximum effect. With people we usually do this for efficiency’s sake (especially in groups); auditory and visual at the same time, followed by some hands-on activity or practice. For dogs, especially for new commands, we’ll say “Fido, sit!” while showing the hand signal, followed by placing or gently pushing if needed.
Repetition is a necessity; I’ve never seen a dog learn a new command after a single exercise, so don’t beat yourself up if you don’t learn that new thing after one try! (I will admit to projecting hard on that one; raise your hand if you’re a former gifted child!)
Lastly, use positive reinforcement. It sticks (pun fully intended) a thousand times better than negative reinforcement with dogs and people. Treats following successes work wonders with dogs. Ours likes these tiny cubes of dehydrated beef liver. A direct analogue may not exist for people though. I can’t see myself having a single raisin every time I write a few words in a post. How do you “treat” yourself for learning?
Want help with training the technology dog in you or your staff? You can find us a scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 13:00:00
@ 65038d69:1fff8852
2025-03-28 13:00:00Two weeks ago I posted “Delete the Technology” talking about the idea of removing entire technological elements from your life, such as smartphones or social medias, as a way to simplify. Little did I know one of those elements in my life would soon be deleting me…
Story time! While at my desk last week I saw I had an email from Instagram about the ScaleBright account. It had been suspended due to being connected to my personal Facebook account, which was an admin on a Facebook Page for an old business (closed 5+ years ago), which was currently suspended for “violating community guidelines”. I could of course appeal this decision, which I did, and during the process it was explained that the offending Facebook Page was suspended by one of their automated systems. Also, because the ScaleBright Instagram account was connected to my personal Facebook account, it too had been suspended, as well as my associated personal Instagram account. To reiterate, the causal chain of events was:
- automated suspension of an old, disused Facebook Page, which caused
- automated suspension of the ScaleBright Instagram account, which caused
- automated suspension of my personal Facebook account, which caused
- automated suspension of my personal Instagram account
After appealing the suspension of the ScaleBright Instagram account another automated system released it, saying the suspension was in error. In theory this should have automatically released my personal Facebook and Instagram accounts. As luck would have it, this did not happen. Those accounts are still suspended.
The instructions from Facebook to appeal where to “log into your (scalebrightsolutions) Instagram account to appeal our decision”. This of course does nothing as that account is no longer suspended. After much searching I was able to find an email address that is supposedly for manually appealing suspensions (appeals@fb.com), but Facebook’s own documentation makes no mention of that address or any other. I’ve sent an email anyway.
Given my earlier suggestion of deleting technology, it may behoove me to take my own medicine and let those accounts go. Do I even need them for anything? I did make extensive use of Facebook Messenger and Marketplace, as well as Groups and Pages. Lots of teams and businesses use these tools exclusively for communication too (such as my local farmer’s market), with little chance of them changing platforms because little ol’ me “doesn’t use Facebook anymore”. But what are my options?
I have two options before me, both of which have downsides. If I can’t successfully appeal, I could let the accounts go and live without those platforms. Or I could create new accounts, but that goes directly against Meta’s terms of service, and I’d risk getting automatically suspended all over again. As of today I’m leaning toward shouting a hearty William Wallace “freedooooom!” and abandoning Meta’s platforms permanently. After all, there are other options for chat and social media that are built to be the antithesis of this sort of centralized authoritarianism, some of which I’m already using.
Nostr is a social media protocol I’ve been using for about a year now. This is different than a platform, such as Facebook, as there is no central ownership or authority for Nostr. Nostr uses a combination of servers (called relays) and apps (called clients), of which anyone can create and use. There are no “official” servers or apps, and while a server operator could ban my account from their server, they can’t ban me from the protocol or anyone else’s servers. If I wanted to I could even create my own private server just for me and my friends. One of the downsides to Nostr is that’s there’s no integrated chat or messaging functions.
For chat I’ve been testing Matrix. It’s similar to Nostr in that it’s a protocol and not a platform, and uses a combination of servers and apps. You can connect to the wider Matrix network, or just your own private server.
The biggest problem with both Nostr and Matrix is that to be useful, people need to use them. This loops us back to Facebook; the people I want to communicate with are there, and have no effective reasons to leave and use Nostr and Matrix instead. I guess I’ll need to brush up on my Braveheart speeches. *Ahem* They may suspend our accounts, but they’ll never suspend our freedom!
-
 @ 65038d69:1fff8852
2025-03-28 13:00:00
@ 65038d69:1fff8852
2025-03-28 13:00:00There aren’t many things in the technology realm that evoke the same level of disgust as having to deal with passwords. For I.T. staff printers are a close second, but for everyone else, passwords are something most would gladly vote off the island. Unfortunately they play a key role (pun fully intended) in verifying your access to your accounts, the same way a physical key verifies your access to your home. But why are they the way they are? And are there any ways we can make them easier to deal with?
When it comes to access security, there are different ways a system can confirm you have access. These are called “factors”, and there are three of them:
Possession Factor: Something you have. This could be a traditional key, a keycard, a fob, or security key.
Inherence Factor: Something you are. Biometrics such as fingerprints and Apple’s FaceID are examples of this.
Knowledge Factor: Something you know. Passwords and PINs are the most common examples.
For knowledge factor methods we have three general options for managing them:
Memorize: This is fine if you only have a few passwords to memorize, but most of us have more than few things to log into, and even more if we include PINs (which are another form of passwords).
Write them down: Much easier than memorizing, especially if you’re making sure each password is unique. A password book is good for up to a few dozen entries but after that will get cumbersome to search through.
Password manager: This is currently the ultimate in password management solutions (hence the name). A password manager can take care of generating, saving, and typing your passwords, as well as your usernames and other form data!
There is one major con to using a password manager; it’s not quite as humanly intuitive as a password book. It’s another system you’ll have to learn and maintain. But the amount of work that it saves and the improved security make it worth the effort. The ultimate goal of password managers is to maximize security and minimize cognitive load.
Okay, you’ve decided to use a password manager. You’ll need to choose from two categories, depending on your level of trust and how much work you’re willing to do. The first are hosted or cloud systems. With these, someone else (the password manager company) is taking care of most of the technical details for you. Bitwarden, 1Password, Proton Pass, Apple Passwords, and built-in browser systems are popular. Sign up for an account, install the browser extension or app on all your devices, and away you go! The downside: you’re trusting these companies to keep your passwords safe, and they’re less than perfect. Do a search for “LastPass leak” for an example. Also, if you’re like me, you may harbour a general distrust of companies (and governments…and banks…and squirrels…and seed oils...wait, what were we talking about?).
Fear not, for the second option requires far less trust in faceless organizations (or rodents). You can self-host your own password manager! The obvious downside is the extra work to set up and maintain it. But hey, no shadowy supervillains up in your passwords! Woohoo! Vaultwarden and KeePass are popular here. And it’s even easier if you have a server like I mentioned in “A Subscription-Free, Cloud-Free Office”.
A few extra notes and further reading on the subject of passwords and security. Regardless of your choice, it’s a good idea to have a plan for granting someone else access to your passwords in case of emergencies, or if something happens to you. If you have a family lawyer, ask them about “digital legacy planning”. Or at the very least leave access instructions with a trusted family member or friend.
If you decide to use a password manager, MFA is still necessary, especially for high-risk accounts like banking and email. MFA will probably get its own article from me in the future.
Finally, you may see hear about “passwordless” and “passkey” systems. These are relatively new, and despite the name, are not complete replacements for passwords. For now, think of them as fancy passwords. Passwords in formalwear. Passwords on the way to the opera. Passwords on the way to a $10,000/plate fundraiser that definitely isn’t a political money laundering operation held at an art gallery that definitely isn’t also a money laundering operation. Squirrel!
If you or your organization want help with your password management, you can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 12:53:02
@ 65038d69:1fff8852
2025-03-28 12:53:02Does your life feel overly complicated? Do most things feel like 10 steps when they used to be 3? Does simply maintaining your existence feel like a hamster wheel with hopscotch squares on the inside? Do you find yourself yearning for “simpler times”? While there are many things in a complex society outside our control, personal technology choices are still within our purview. Maybe it’s time to consider deleting some of the tech from our lives in an effort to simplify.
I worked at a phone shop for some time, and one of the things that surprised me was how many non-smart phones we sold. We had a lot of customers whose only phone needs were calling and the occasional text. Anything their phone couldn’t do could be taken care of on a computer at home or at work, and a smartphone would have been a whole ‘nother stack of skills to learn and maintain. So why not go without one? For less than $100 you can get a plain flip phone from your local phone shop, or hop on your marketplace of choice and get a used one for half that. They’ll take the same SIM card your smart phone does, so simply power down, swap the card over, and try it out for a while!
Social media is another one that you can probably trim down on. How many platforms are you actively using? I’m most likely going to remove Snapchat from my phone as the notifications from Snapchat themselves are annoying, I hardly ever use it, and I’m connected with those I use it with elsewhere. I helped someone recently who uses Facebook to connect with family but has been struggling with the technical aspects of securely maintaining their account. Switching to group texts or another platform those family members are already using may be easier than fighting with Facebook account compromises and their account recovery processes.
You may even consider abandoning social media completely. “I’m not on social media” has become less the exclusive domain of luddites and is certainly not only spoken by older generations. Any Gen Zers who took part in the “nose cover” trend early this year will understand. Try going on a social media fast for a few weeks (or even a few days) and see if you feel the need to return.
Using myself for another example, I bought a smartwatch about 3 years ago and wear it fairly regularly. But the work to make sure its charged, keep up with the changes, and any manual maintenance items has me thinking I won’t be replacing it when it dies. The nice-to-haves it brings aren’t worth the trouble.
A final hot take: In your workplace, how many staff’s only interaction with technology is time tracking or timesheets? Paper timesheets may be an option. I know, I know, Hell has frozen over and the tech guy is talking about switching something from digital to paper. But my job is supposed to be to guide toward efficiency. If bludgeoning your blue collar staff into the cyberpunk dystopian future of a spreadsheet (or even worse, a geofence-powered time tracking app on their phones) turns out to be more work than entering a handful of numbers off of paper timesheets, maybe paper is the more efficient (and humane) option.
If you like the idea of deleting technology at work or at home and want some help with it, you can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 12:53:02
@ 65038d69:1fff8852
2025-03-28 12:53:02Apple held one of their regular events last week and announced the iPhone 16. The inevitable repeating questions ensued. Should you upgrade your phone? Is it time? Is it worth it? What about Android users? Should I switch to an iPhone? Should I switch to an Android? If you’re looking for a short answer: no. If you have an attention span longer than that of a ferret, there is some nuance to be had.
First let’s define “upgrading”. In this context I define it as buying a new phone before your current one has reached the end of its useful life. Your current phone is working just fine, there’s nothing wrong with it, but you buy a new one anyway.
There’s nothing morally or ethically wrong with upgrading, but practically it’s pointless. Phone cameras plateaued 10 years ago (around the time of the iPhone 6 series), and the rest of the hardware a few years after that. Aside from some edge cases, the current lines of phones will do the same things for you as a 10 year old design would. Look up some sample photos from an iPhone 6. Then look at similar photos taken with the iPhone 15 or 16. They’re functionally the same. “No, the new ones are better! You can tell when you zoom in 100x or get a wall-sized poster print!” Those are the edge cases I talked about. You’re posting fur baby updates for grandma on Facebook and low-effort thirst traps on Instagram. You don’t need 48MP.
With the launch of the iPhone X and Samsung S8 in 2017, we saw the removal of the physical home button and entrance into the current epoch of “plain rectangle with a touch screen”. Which is excellent, because you no longer have to spend hours agonizing over which phone to buy. Pick a screen size, pick your budget, and you’re done! You are the proud owner of a functioning plain rectangle that will continue to function until the manufacturer stops supplying security updates (typically 5 to 7 years).
To summarize, don’t bother replacing your phone unless it: a) dies, b) the battery dies and a replacement is 50% or more of the cost a new phone, or c) it’s no longer getting security updates.
Since this conversation was started by the iPhone launch that’s mostly what I’ve talked about, but this applies to mainstream Android phones as well. Samsung and Google promise 7 years of updates for their current gen lines. There’s no need to upgrade, only replace.
Lastly, if you’re on an Android, don’t bother switch to an iPhone. It’s in no way “better”, and the mental load of learning a different system will have you clawing at the walls of your padded cell. Same goes for the iPhone users; don’t bother switching to an Android. Either switch would be like trading in your perfectly good rust-bucket for a Toyota because you think you’d have to fix it less…wait…no…that’s a bad example…
-
 @ 65038d69:1fff8852
2025-03-28 12:50:13
@ 65038d69:1fff8852
2025-03-28 12:50:13Have you heard the phrase “death by committee”? The idea being put forward by the phrase is that a project or task is doomed to fail if given to a hierarchically-flat group instead of an individual (see also “death by a thousand cuts”). While an individual decision-maker will almost always be more efficient, most organizations that are not for-profit (and even many that are, such as publicly traded corporations) are run by a governing body. If you find yourself in this situation you may be asking yourself, “how do we even get anything done?” As with many things, the answer is relatively simple, but can be extremely difficult to implement, for the exact reasons we just went over.
First, let’s define roles:
Governing body: This will most commonly be a council, board, or committee. Aside from formal meeting roles (see Robert’s Rules of Order), we’re going to assume the members only have authority as a democratic group.
Operations or staff: Everyone in the organization who is not part of the governing body. This includes contractors, consultants, and volunteers. We’ll use “operations” and “staff” interchangeably as euphony dictates.
Executive leader: This person may have the title of CEO, CAO, Director, or Manager, depending on the scale of your organization. For the purposes of this article, we’re going to include them in “operations”.
Next comes responsibilities. The governing body is responsible for mission, policies, and direction. Operations is responsible for procedures, tasks, and reports.
(A quick note; we’re going to assume all of these things are written. The value of the written word is a common theme here at ScaleBright, and I will most likely die preaching on the subject. See the previous entries under “Writing Things Down Is for Boys Too”, “Paper Copy Please!”, and “One Skill to Rule Them All”
Let’s also define the responsibilities:
Mission: The reason the organization exists, or what it’s trying to accomplish. This may be summarized in a formal mission statement.
Policy: A formal set of guidelines for the actions and behaviour of the governing body and operations. Policy does not usually include specific procedures or tasks, unless governing law requires it (i.e. harassment reporting and investigation sections of HR policies).
Direction: Governing body decisions, requests, and any other instructions passed to operations.
Procedures: A formal set of specific instructions for tasks.
Tasks: Activities that are carried out.
Reports: Information passed from operations to the governing body. Usually take the form of requests for decisions or post-task summaries.
Now that we have definitions for everything, let’s walk through how something would get done in some hypothetical scenarios.
Scenario 1: The volunteers (operations) at a food bank see that they have a need for more refrigerated food storage space. They prepare a report (task) using a decision request template (procedure) outlining the need as well as options for solutions (additional refrigerators or a walk-in cooler). The report is given to the manager (executive leader) for review and presentation to the board (governing body). The manager presents the report, and the board weighs the request based on the food bank’s mission and available resources. The decision is made to purchase additional refrigerators (direction) and the manager and staff follow their purchasing procedure to buy them, install them, and utilize them (procedures and tasks). Once they’re up-and-running, they send a brief report back to the board (via the manager) letting them know the direction was acted on and the tasks were completed.
Scenario 2: The council (governing body) of a municipality wants to build a new multiplex. Municipal law (policy) requires public consultation, so they ask (direction) their CAO (executive leader) to carry it out. The CAO passes the direction onto their staff, who follow their procedures to carry out the public consultation (tasks). Once the public consultation is over, the information is compiled (reports) and made available to the council for assessment.
A final note; both the governing body and operations should be fully aware of the other’s responsibilities. If staff know a potential request goes directly against policy, they can save everyone time by finding an alternative that doesn’t. If the governing body knows how long a particular procedure takes to complete, they won’t need make constant requests for updates.
If you’d like help implementing any of this in your organization, you can find us at scalebright.ca.
-
 @ 3a8a16a7:f4c3b0b4
2025-04-29 22:46:32
@ 3a8a16a7:f4c3b0b4
2025-04-29 22:46:32 -
 @ 65038d69:1fff8852
2025-03-28 12:38:37
@ 65038d69:1fff8852
2025-03-28 12:38:37PDFs are everywhere, and pretty much everyone has used one at some point. How did we get here? What even are they? And is there anything we can do to make using them easier?
PDFs are both a type of file and a standard. The Portable Document Format was created by Adobe in the 90s, and became an open standard under the ISO (International Organization for Standardization) in 2008. It’s creator’s goals were to create a document format that could be opened on any device, regardless of platform, screen size, etc.
They were mostly successful. PDFs are now one of the best ways to send someone a document without having to worry about them being able to open it. Windows, MacOS, Linux, iOS, Android, e-readers, and even embedded devices like car infotainment systems and fast food menu screens can display them. Most email systems can open them without you having to download the file first.
Making a PDF is usually a straight-forward process. Most document software (Word, Google Docs, Pages, etc.) have a built-in export feature that will save the current document as a PDF. Or if you’re starting with paper, your scanner will spit out a PDF file. Then you can send that file to whoever you like. This is where you might encounter the most common problem I’ve had to help users with.
PDF files are not designed to be edited. Yes, technically they can be, but it’s a rough process that rarely gives us the results we want. Same with attempting to convert a PDF back into whatever format the file was originally created in. Especially if you’re scanning a paper document. Even the fanciest, most expensive OCR (optical character recognition) software can’t turn a printed document back into an exact replica of the original. If someone sends you a PDF and you want to edit it, ask them to send you the original file instead. If they can’t, or won’t, that’s most likely on purpose.
This is an intentional feature of PDFs. If you want to send a document to someone and you don’t want them to be able to easily edit it (i.e. a contract or an invoice), PDF’s finalized nature makes it an excellent choice. The standard even includes options for encryption and passwords if you really want to limit the receiver’s ability to tamper with a secure document.
Speaking of secure documents, signatures and forms are also features of the PDF standard. This lets us do things like fill out and sign legally binding documents without having to travel to do so in person. Electronic signatures are well established in Canadian law and most other jurisdictions.
Last feature: printing. PDFs are an excellent way to make sure the physical attributes of a document remain unchanged when sent to someone. If a document is meant to be printed on a particular size of paper or in a particular orientation, these things are saved when the PDF is created.
If you want to smooth out your office’s processes that involve PDFs or other digital documents, or if you just need a little help with them, you can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 12:38:37
@ 65038d69:1fff8852
2025-03-28 12:38:37A common question interviewers ask is variations of, “If you could impart one piece of advice to everyone listening, what would it be?” I would answer that in the context of the workplace, reading comprehension is the base skill that underpins everything else.
Why reading comprehension? Most instructions come in the form of the written word. In the workplace, think of policies, procedures, notices, warning labels, and equipment instructions. Ikea has made an attempt at word-less assembly manuals, but I’m willing to bet most who’ve used them would rather they include at least some written information.
Humanity has been aware of the value of writing things down for most of history (see “Writing Things Down Is For Boys Too” for my arguments for the written word). And if we’re going to write things down, we need to be able to read (and comprehend) as well.
If you’re still not convinced, consider the skills training that are built on top of reading comprehension. Critical thinking, effective communications, leadership development, problem-solving, and most things technology related all depend on a functional level of reading comprehension.
The solutions for this are all underpinned by the same concept: practice. To improve your reading comprehension, practice reading and thinking about what you’ve read. Ideally in multiple forms. Short, medium, and long form are all important and will work different higher-order skills. For example, reading long form will teach patience and more complex analysis. If you’d prefer something more formal, many community libraries have adult literacy programs and most post-secondary institutions have relevant classes as part of their academic upgrading or essential skills programs.
I should point out that I see the irony in the fact that I include audio versions of these articles for those who’d rather listen than read. I’m also an avid audiobook consumer. My excuse is that most of my listening is done while carrying out mentally passive activities, like household chores. So you won’t receive any judgment from me if you continue to listen instead of read.
-
 @ 65038d69:1fff8852
2025-03-28 12:38:37
@ 65038d69:1fff8852
2025-03-28 12:38:37This week would have normally been a “People” category post, but with the news of Telegram CEO Pavel Durov’s arrest in France, I thought it would be a good opportunity to talk about secure communications instead.
When we say “secure communications” you probably imagine a stereotypical spy movie scene where a character at a payphone delivers the line “…is this line secure?”. While the days of ubiquitous payphones are mostly past us, many of us still like the idea of having at least private conversations with others.
We’re going to get the most technical and difficult parts of all this out of the way first. The difference between public, private, and secure communications, and the most difficult of all, figuring out what you want.
Public communications: Social media posts, blog posts, news media, and advertisements are public. They’re meant for a broad audience and we typically don’t care who sees them.
Private communications: Traditional telephone calls and physical mail are private. They’re meant for only the sender and receiver to see, but we don’t usually go out of our way to stop others from seeing the contents (i.e. we leave our mail on our car seats and kitchen tables).
Secure communications: Paper cheques, tax filings, and love letters. We’re willing to take extra steps to make sure others don’t see them (i.e. security envelopes and in-person delivery).
Most of the time private will do just fine. Apple’s iMessage and SMS or RCS everywhere else for texting does the job. Facebook Messenger, WhatsApp, and email are also fine. The average ne'er-do-well would need to steal your device to get access, and even then screen locks and passwords will stop most of them.
Platforms like Facebook Messenger and Signal advertise something called “end-to-end encryption” (abbreviated “E2E”). This means that before the message is sent it’s scrambled in such a way that only the receiver can unscramble it to read it. The problem is that we’re required to trust the provider, whether it be Facebook, WhatsApp, or Apple, to not lie and spy on us. In the case of Telegram, France arresting their CEO pushed Telegram over some people’s risk boundary as Mr. Durov may be willing to trade his freedom for government access to everyone’s messages. Who you decide to trust is entirely up to you.
If your answer is “I trust none of them!”, you may be willing to put in the work to set up secure communications. The idea is to host the platform (or at least the security functions) yourself so you don’t have to trust someone else to do it for you. As of the posting of this article, there are 3 systems I can recommend. They all come with tradeoffs and a fair amount of work to set up.
Email with PGP: PGP is an E2E system for email. Most email clients have a built-in way to use it. The hardest part is usually getting your contacts you want to use PGP with set up as well. It can also be difficult to use on mobile devices.
SimpleX: While quite secure, this system is still very much in testing. It’s also difficult to set up and use in a way that doesn’t rely on the creator’s servers (remember the trust issue?).
Matrix: This one takes a bit of work to set up and can be slow depending on your internet connection, but it’s the most full-featured and mobile-friendly of the systems I’ve tested. The biggest tradeoff is that you’ll need your own server.
Want help setting up secure communications for your business or personal group? You can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 12:24:05
@ 65038d69:1fff8852
2025-03-28 12:24:05Since the dawn of ubiquitous internet, websites have been vying for our attention. The intention behind commercial websites was harmless enough; to inform you of products or services available, like a stereotypical medieval street sign indicating blacksmith, tavern, or baker. But this quickly turned into an arms race with Madison Avenue advertising types employing every dirty trick they could think of to get eyeballs on screens. This led to what we have today, with our websites looking like Times Square or gossip magazine covers. And all this comes at a price; a website design and build for a small to medium sized org from a professional design firm will usually cost between $10,000 and $20,000.
I’m here to rescue you from this, and prove to you that your website can be done for a tiny fraction of that cost. Not only that, but it will be easier to read, require almost no maintenance, be extremely secure, and dirt cheap to host.
Sound too good to be true? You’re right to be skeptical. So I proactively put my words into action and built a version of the ScaleBright website using this framework. You can see it (and easily find your way back to this article) at simple.scalebright.ca.
Are you impressed? Shocked? Disappointed? “But Taylor, how am I supposed to convince my potential customers that I’m a serious business worthy of their patronage with a website like this?!” You probably already know that most of your business comes from happy customers referring others to you. When was the last time someone told you they came because they liked your website? Most likely never. So save yourself the $20,000, or even better, reinvest it into directly improving your services or broadening your product selection. Your customers will appreciate that volumes more.
Interested in a website like this? You can find our contact information at scalebright.ca, or if you prefer, simple.scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 12:19:56
@ 65038d69:1fff8852
2025-03-28 12:19:56On a Twitter thread about a fairly technical product a customer asked if the creator would consider making a paper version of the documentation. Their discussion got me thinking; is there a market for paper manuals for digital systems in our digital age?
Paper manuals for digital things isn’t a new idea, but it isn’t old either. 1950’s IBM mainframes had paper manuals, and books on Microsoft 365(https://www.amazon.ca/Teach-Yourself-VISUALLY-Microsoft-365/dp/1119893518) have been a big hit in offices I’ve worked with. They have a number of advantages: - They’re far less prone to failure or inaccessibility (power outages, etc). - They can be easier to find. A small shelf of manuals is simpler to look through than computer folders full of files. - For some, they can be easier to read and absorb. - It can be easier to follow along with instructions visible alongside your computer screen.
There are some disadvantages though:
- They’re slow or potentially impossible to update.
- They’re expensive to create and distribute.
- They aren’t searchable.
- You can include screenshots and photos, but not video.
Even while writing those out I was able to think of ways to work around or assist with those cons: - If in binder format, individual pages or sections could be replaced. - While not as fast as search, a back matter index could help. - QR codes linking to videos would be quick and easy to use.
The manuals I’m imagining wouldn’t be generic (i.e. the Microsoft 365 one linked above); they would be for processes specific to your org. For example, “how to fill out and submit a timesheet” or “how to troubleshoot our internet”. It might make sense to create a demo for people to check out in person…let me know if this is something you’d like to see.
The final question is financial viability. How much would you pay for a manual (or set of manuals)? How much would you pay for updates? Do you have staff capable and willing who you could pay to do this, or would you need hire someone external?
If any of this sounds interesting to you, if you have questions, or if you think I’m crazy and want to tell me so, you can find contact details on our website at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-28 12:10:35
@ 65038d69:1fff8852
2025-03-28 12:10:35Even if you don’t consider yourself a “technology person” you’ve probably experienced “cloud” outages. We’ve had some large ones in the news recently; CDK Global last month (that was the car dealership one), Crowdstrike last week, and AWS seemingly always (they have so many they’ve become genericized and a meme).
Maybe you’re tired of dealing with these sorts of outages, or maybe you don’t like the idea of AI in everything. (I wrote a bit about this in “Is It Time for Linux on the Desktop?”.) There are options for your office, most of which are free, though they do come with some trade-offs.
The biggest is that you’ll be trading some of your OpEx for CapEx. Larger organizations probably won’t care as much as they’ll have plenty of both already, but if your technology budget is only a few thousand dollars a year it might be a large shift to go from spending a predictable, smaller amount monthly to larger amounts every few years.
The other is that you’ll need dedicated I.T. support and training. Again, if you’re a larger org you probably already have this. Not all of the software and systems I’m about to show you are as simple to set up as M365 or Google Workspace, and most of them don’t come with any automated maintenance.
Let’s start with a productivity suite (or office suite), since we’re already using one! The slides for this video were made in Impress, which is part of the LibreOffice suite. LibreOffice is open source and free, which means no subscription fees! Yay!
LibreOffice also includes Writer, a word processor, and Calc, a spreadsheet editor. As you can see, they’re quite similar to their Microsoft counterparts, but there are enough differences that your office will experience some productivity loss while your staff learn the differences.
You may have noticed that the task bar along the bottom doesn’t look like Windows. That’s because it isn’t! This computer is running Linux Mint, an operating system that, like LibreOffice, is open source and free. It also has the advantage of being very light; this demo is running on the equivalent of a 15 year old computer, so no need to buy $1000+ laptops just for office tasks. Using it is very similar to using Windows; there’s a bar along the bottom with a clock and icons on the right, running programs and shortcuts on the left, and a menu with power, settings, and installed programs. There’s also a file browser with all the usual folders.
Speaking of files, you may find yourself missing something like OneDrive or Google Drive. There are several open source and free alternatives for that too! This demo is using Nextcloud, and I use it for my business as well. It works very similar to OneDrive; I have my folders on this computer synced as well as access to shared folders.
Central file storage will be one of the new sources of CapEx. You’ll need a server of some kind for things like Nextcloud, as well as external backups. It doesn’t need to be a giant $20,000 rackmount unit; for most small offices something like a Start9 server or Intel NUC mini-computer with some USB drives will do great for $1,000 to $2,000 every 5 years or so. These servers can also do lots of other things we won’t cover today.
Next up is email. I recommend Thunderbird; it’s open source and free, and made by the same people as the Firefox web browser. It does email, contacts, calendar, and tasks, and can do chat, but I have a different recommendation for chat. Email service is one of the things we have to compromise on in our “cloud-free” plan and use a third party service for. Business-grade email service will cost anywhere from $15-$150/year/user depending on usage volume, features, and security threat models.
Last is chat and conferencing. This is another item we’ll make some compromises on. You’ll still be joining meetings on Zoom, Teams, WebEx, etc that others invite you to, but you can set up your own internal communications system without using any of those. Signal and Telegram are reasonably trusted third parties outside the “giant evil corporation” spheres, or if you have a server, SimpleX and Matrix are options. For demo purposes I have a Matrix system set up. You can do direct messaging, groups, and audio and video calls. Sending media and files are also supported.
This wasn’t meant to be an exhaustive list, so I’ve skipped over a few items (document signing, bookkeeping, and payment systems got cut from this demo), but the idea was to show you some of what an alternative office setup could look like. If any of this sounds interesting to you, reach out for a consultation. You can find us at scalebright.ca.



