-

@ a39d19ec:3d88f61e
2024-10-27 10:26:03
**October's daily driver is the ana-digi Casio ABX-53 Twincept with module 1326. It features are world time, stopwatch, alarm and a databank for contacts.**

## Design
I have the gold/silver colored variant with a metal band. The watch has an analog clock and a floating display with the features listed above. Best thing is the "slider" mode that switches digital functions permanently.
## Storytime
My log tells me that i bought the watch 6 years ago on a local flea market for close to nothing. It was in a bad condition and needed a new battery and some love. Sure enough it works fine since then.
Most badass feature is that the analog hands are moved electronically not mechanically.
Fun fact is that even my wife likes the floating display. First time she saw it I heard her say "Das ist echt cool", meaning "thats really cool".
-

@ eac63075:b4988b48
2024-10-26 22:14:19
The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also [addressing her Bill No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
[(PT-BR version here)](https://www.eddieoz.com/drex-e-o-fim-do-dinheiro-fisico-no-brasil/)
## **What is a CBDC?**
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their **programmability**. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
## **Practical Example: The Case of DREX During the Pandemic**
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, [the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence](https://youtu.be/cjUz2VEk4co?feature=shared&t=484&ref=eddieoz.com), limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
## **How Does China's Social Credit System Work?**
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, [including financial behavior, criminal record, social interactions, and even online activities](https://journals.sagepub.com/doi/full/10.1177/1461444819826402?ref=eddieoz.com). This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, [they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods](https://www.businessinsider.com/china-social-credit-system-punishments-and-rewards-explained-2018-4?ref=eddieoz.com), or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
## **DREX and Bill No. 3,341/2024**
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy ([Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG](https://www.camara.leg.br/proposicoesWeb/fichadetramitacao?idProposicao=2259342&fichaAmigavel=nao&ref=eddieoz.com)) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, [Julia drafted her bill, PL No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
## **Risks and Individual Freedom**
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
## **The Relationship Between DREX and Pix**
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
## **International Precedents and Resistance to CBDC**
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
## **Bill No. 3,341/2024 and Popular Pressure**
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
## **What’s at Stake?**
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
## **A Call to Action**
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-

@ 592295cf:413a0db9
2024-10-26 13:39:00
[Week 21-10]
I thinks that Saylor is on right, don't trust verify, is bullshit
Bitcoin is a financial tool!
I think it's good for me to get away from social media once a week.
I could do things outside, like walking.
Take pictures of the landscape. The weirdest thing is when the alarm calls you up in an hour.
Fiatjaf wants a cache client. I feel like I can do it, I have the set to do it,
but nostrudel is no longer working, so it's a little murky.
Next nostrudel does not accept changes to settings
(It works now!), so maybe i can think something.
I want to make a corny chat, test, read this article.
Nostr doesn't work with a vpn because relays don't know who you are. jokes aside, some clients have difficulties.
### **I couldn't take pictures of the landscape if I didn't take the wind blades.** Small local controversy.
Missing the point of content creator. Simply for final user, Simply for the creator, new feature, no missing nothing.
I'm trying to limit everything to writing for a week. I almost did. Maybe another week can do well.
Meanwhile I updated apps like Amber and Voyager, coracle, nostrmo.
The experiment continues with open vibe following the trending of Nostr. I'm following almost 120 npub.
He'll stop, I don't know, possible he's already reached the limit.
You still can't block words on the Nostr side of Open, strange thing.
The app doesn't count the follow well, still some problem cleaning the cache seems that it doesn't need.
After a while open and close and seems updated.
I wanted to try open librarian, but I was busy sending fake zap on Nostr.
This morning i try and It keeps giving me error 500 when I try to connect to a relay.
I hate when a profile follows everyone indistinctly, why does everyone follow? and in voyage, I read with WoT setting,
I probably have to do unfollow. There must be an indication in which not include the followers of this person in the web of trust,
I would do it by default if you follow more than 600 people.
WoT on Nostr Visualized [post on stackernews](https://stacker.news/items/739477)
-

@ 8f69ac99:4f92f5fd
2024-10-25 09:49:56
O recente relatório do Banco Central Europeu, [*As Consequências Distribucionais do Bitcoin*](https://papers.ssrn.com/sol3/Delivery.cfm/4985877.pdf?abstractid=4985877&mirid=1&type=2), recicla a velha narrativa de que o Bitcoin é um activo especulactivo que causa desigualdade de riqueza sem oferecer benefícios económicos tangíveis. Os autores, Ulrich Bindseil e Jürgen Schaaf, desfilam as críticas de sempre, afirmando que o Bitcoin falhou como sistema de pagamento global e que se transformou numa bolha, enriquecendo os primeiros utilizadores à custa da sociedade. Também lançam uma pitada de alarmismo ambiental e argumentam que o Bitcoin ameaça a democracia.
Como era de esperar, o BCE continua apegado às mesmas concepções erradas que já foram desmentidas inúmeras vezes. O que este relatório não percebe, de forma espectacular, é que o Bitcoin não é apenas mais um activo; é uma tábua de salvação para aqueles desiludidos com os sistemas fiduciários inflacionários e governos corruptos. Ao longo desta análise, vamos desmontar os argumentos do BCE, expondo não só o seu profundo desconhecimento sobre o Bitcoin, mas também a ignorância gritante em relação ao seu potencial de conceder soberania financeira a milhões de pessoas em todo o mundo. O BCE retrata o Bitcoin como uma ferramenta elitista, mas ignora como as suas próprias políticas têm sistematicamente enriquecido alguns poucos à custa da maioria. Vamos então entrar no assunto.
### 1. **Deturpam o Papel do Bitcoin como Sistema de Pagamentos**
> "O Bitcoin nunca foi usado em grande escala para transacções legais no mundo real."
Que originalidade. Os autores descartam a utilidade de pagamento do Bitcoin com um gesto, mostrando que não compreendem a Lightning Network, que facilita transacções rápidas, baratas e escaláveis a nível global. Certamente, talvez os europeus ainda não estejam a comprar os seus cafés com Bitcoin, mas isso é irrelevante. O Bitcoin é uma tábua de salvação financeira em locais como El Salvador e em inúmeras outras regiões que sofrem com sistemas fiduciários em colapso.
Esta visão eurocêntrica, como se todo o mundo partilhasse das mesmas condições económicas, reflecte uma total falta de perspectiva. Os autores seleccionam dados a dedo para encaixar na sua narrativa anti-Bitcoin, enquanto convenientemente ignoram os milhões que utilizam o Bitcoin para escapar à hiperinflação e a regimes autoritários. A afirmação de que o Bitcoin não é usado para transacções "legais" é não só enganosa, como revela a sua ignorância sobre as necessidades reais de quem vive fora da sua bolha privilegiada.
---
### 2. **Deturpam o Bitcoin como activo Especulactivo**
> "O Bitcoin não gera qualquer fluxo de caixa (como o imobiliário), juros (como as obrigações) ou dividendos (como as ações)."
Parabéns, BCE, acabaram de perder o ponto fulcral do Bitcoin. Esta afirmação mostra uma falta de entendimento fundamental do que torna o Bitcoin único. Ao contrário de imóveis ou obrigações, o Bitcoin é uma forma alternativa de dinheiro—não algum esquema de rendimento passivo.
O valor do Bitcoin não depende de gerar dividendos ou juros, mas advém da sua escassez, descentralização e resistência à censura. Ao reduzir o Bitcoin a modelos de activos tradicionais, o BCE ignora o paradigma económico revolucionário que este oferece: uma escapatória aos sistemas fiduciários inflacionários, particularmente para os milhares de milhões de pessoas presas em sistemas financeiros corruptos.
Ao tentar enquadrar o Bitcoin em modelos convencionais, os autores revelam a sua preguiça intelectual. A utilidade do Bitcoin reside no seu potencial como dinheiro sólido, e não como um veículo de investimento para especuladores atrás de rendimento.
---
### 3. **Deturpam os Custos Ambientais e Sociais da Mineração**
> "A mineração de Bitcoin consome muita energia e causa danos ecológicos e sociais."
Ah sim, o argumento gasto sobre o consumo energético. Enquanto a mineração de Bitcoin realmente requer energia, os autores omitem convenientemente os enormes avanços que a indústria fez em direcção à sustentabilidade. Cada vez mais, os mineradores de Bitcoin recorrem a fontes de energia renovável e, em alguns casos, estão até a ajudar a financiar infraestruturas de energia verde.
A ironia aqui é que o BCE, uma instituição que fomenta políticas que inflam bolhas imobiliárias e de acções, de repente está preocupado com os custos sociais e ambientais. E mais, ignoram como a procura de energia barata por parte do Bitcoin incentiva realmente o desenvolvimento de soluções energéticas sustentáveis. Num mundo onde os sistemas fiduciários alimentam a ganância corporativa e a degradação ambiental, o Bitcoin está posicionado para impulsionar uma verdadeira inovação na energia verde.
---
### 4. **Visão Deturpada da Redistribuição de Riqueza**
> "Os efeitos de riqueza do Bitcoin beneficiam os primeiros utilizadores à custa dos que chegam mais tarde e dos que não o possuem."
Isto é pura comédia. Aparentemente, o BCE acabou de descobrir que os primeiros investidores em **qualquer** activo beneficiam mais do que os que chegam depois. Não é assim que os mercados funcionam? Os primeiros investidores em acções, imóveis e ouro beneficiam de forma desproporcional—mas, curiosamente, isto só se torna um problema quando se trata de Bitcoin.
O que o BCE realmente teme é que o Bitcoin democratize a riqueza de uma maneira que eles não conseguem controlar. Com o Bitcoin, não precisas de acesso privilegiado para participar. Não precisas de um corretor _XPTO_ ou de permissão dos guardiões financeiros. Ao contrário das próprias políticas do BCE—concebidas para inflacionar a riqueza dos já ricos através de bolhas imobiliárias e do mercado de acções—Bitcoin oferece um campo de jogo nivelado para qualquer pessoa com uma ligação à internet.
---
### 5. **Sensacionalismo: a Ameaça à Democracia**
> "O aumento perpétuo do preço do Bitcoin empobrece o resto da sociedade e põe em risco a democracia."
Aqui, os autores entram no melodrama, avisando que o aumento do preço do Bitcoin põe em risco a democracia. É fascinante como ignoram a verdadeira ameaça à democracia: as suas próprias políticas inflacionárias.
Na realidade, os sistemas fiduciários, através da inflação incessante e do _quantitative easing_, erodem sistematicamente a riqueza dos mais pobres e da classe média. Os ricos, com as suas carteiras de acções e imóveis, conseguem resistir à tempestade. Mas o trabalhador comum, cujo salário compra cada vez menos a cada ano, é esmagado. Se há algo que ameaça a democracia, é o poder descontrolado do BCE de desvalorizar a moeda que as pessoas usam para viver. Bitcoin, por outro lado, dá às pessoas uma reserva de valor incorruptível e descentralizada, imune aos caprichos dos banqueiros centrais.
---
### 6. **Percepção "Equivocada" da Escalabilidade do Bitcoin**
> "As transações em Bitcoin na blockchain são lentas e caras."
Esta crítica ignora a realidade do progresso tecnológico. As transacções on-chain de Bitcoin nunca foram pensadas para compras diárias—para isso é que serve a Lightning Network. Os autores agarram-se a esta crítica desactualizada, como se o Bitcoin fosse uma entidade estática que não evoluiu na última década.
Soluções de segunda camada como a Lightning Network permitem transacções quase instantâneas e de baixo custo, tornando o Bitcoin escalável de maneiras que o BCE se recusa a reconhecer. Mas porque deixar que os factos estraguem uma boa história de medo?
---
### 7. **Ignoram o Impacto Económico Global do Bitcoin**
> "O Bitcoin não tem casos de uso benéficos para a sociedade."
Esta afirmação é tão limitada que é quase impressionante. A utilidade do Bitcoin não se trata de conveniência para os ocidentais comprarem café; trata-se de sobrevivência para as pessoas em países como a Venezuela, o Líbano ou a Nigéria.
Quando as moedas locais colapsam e as pessoas não podem confiar nos seus bancos, o Bitcoin oferece uma saída. Ao descartar o impacto real de Bitcoin sobre os milhares de milhões (mais de metade da população mundial) de pessoas que vivem sob regimes opressivos e em hiperinflação, o BCE revela um embaraçoso viés ocidental e falta de empatia. O Bitcoin é mais do que apenas um activo alternativo, é uma tábua de salvação para pessoas em todo o mundo que sofrem com sistemas fiduciários falhados.
---
### Conclusão
O relatório do BCE recicla críticas desactualizadas e já desmentidas, não conseguindo ver o panorama geral. Aplica modelos financeiros antigos a uma **nova forma de dinheiro**, ignorando o potencial de Bitcoin para democratizar o acesso a um sistema financeiro justo, descentralizado e incorruptível. Enquanto os bancos centrais, como o BCE, continuam a desvalorizar moedas e a inflacionar bolhas de activos (e parece que vem ai mais...), Bitcoin oferece às pessoas um caminho para a soberania financeira.
O verdadeiro valor de Bitcoin não se encontra nas críticas superficiais e eurocêntricas do BCE. O seu valor reside na capacidade de fornecer liberdade financeira a indivíduos em todo o mundo, libertos da má gestão de governantes e banqueiros centrais. Se há algo que ameaça a democracia, é o historial do BCE de enriquecer alguns poucos à custa de muitos. Bitcoin, por outro lado, oferece um futuro mais justo—um onde são os indivíduos, e não as instituições, que têm o poder.
Alguma literatura:
- [Universidade de Cornell - Bitcoin pode impulsionar o desenvolvimento de energias renovaveis](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development)
- [Aldeias em Africa com electricidade atraves de Bitcoin](https://gridlesscompute.com/2022/09/28/21st-century-villages/)
- [Relatorio de 2023 sobre a Lightning Network da River](https://river.com/learn/files/river-lightning-report-2023.pdf)
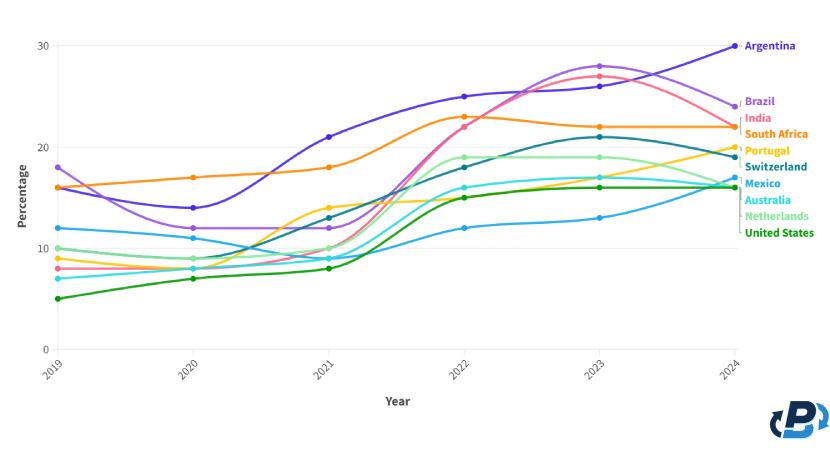
- [Adopcao de Bitcoin por Pais](https://plasbit.com/blog/bitcoin-adoption-by-country)
---
_Photo by [Taras Chernus](https://unsplash.com/@chernus_tr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash]("https://unsplash.com/photos/man-in-teal-hoodie-with-i-love-you-text-euaivxORAm8?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_
#Bitcoin #BCE
-

@ dd32f3e0:498f1df9
2024-10-25 01:42:06
eyJfaWQiOiJkMmVkZDBkMy0yZmM3LTQxNWYtYTA5MC1iY2Q2ZDE2YTc2YjYiLCJwdWJsaWNLZXkiOiJkZDMyZjNlMDgzNDdlYTYzM2U2MzZkODlhMjMzOWQ0N2IyOTM2MWZkZTQ3MTZjZjNhZTBhMzhhYTQ5OGYxZGY5IiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJtYXJrZXRQcmljZSI6bnVsbCwiZml4ZWRQcmljZSI6MTUwLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6NTAwLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoibmljZSB0cmFkZXIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMTo0MjowNi4yNzBaIn0=
-

@ 6f0ba1ef:58eb4351
2024-10-25 01:16:41
eyJfaWQiOiIzMjFkMjkyNi0xOGUyLTRjYTgtOWIwYy0xNGMwNWExZDc4ZTAiLCJwdWJsaWNLZXkiOiI2ZjBiYTFlZjc4YjE3ZTVkMjNkMmVjZDlkYWNlNmJhMzBlODI1NzUxMGY0NmYxNjA0NGUyZjY5ZjU4ZWI0MzUxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MywibWFya2V0UHJpY2UiOjE1Ny40NiwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjoxMCwibWF4QW1vdW50IjoyMDAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiJ2ZXJ5IGZhc3QgYW5kIGVhc3kiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMToxNjo0MS41MDBaIn0=
-

@ c631e267:c2b78d3e
2024-10-23 20:26:10
Herzlichen Glückwunsch zum dritten Geburtstag, liebe *Denk Bar*! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt.
Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen.
Seit dem Start der *Denk Bar* vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. [Damals notierte ich](https://denkbar.substack.com/p/andreas-denk-bar-eroffnet):
> «Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.»
Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden.
Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen [«inneren Totalschaden»](https://denkbar.substack.com/p/innerer-totalschaden) hatte ich mal für unsere Gesellschaften diagnostiziert.
Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der [Gleichschaltung](https://denkbar.substack.com/p/warum-trotzdem-dieses-handeln), das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute.
Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend.
Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns.
---
**Danke, dass du diesen Weg mit mir weitergehst!**
-

@ 6f0ba1ef:58eb4351
2024-10-22 23:31:47
eyJfaWQiOiJjYmE4N2YyNS1jZjRkLTRkNzgtYmIwZS05YjNhNzA0MWVjNGIiLCJwdWJsaWNLZXkiOiI2ZjBiYTFlZjc4YjE3ZTVkMjNkMmVjZDlkYWNlNmJhMzBlODI1NzUxMGY0NmYxNjA0NGUyZjY5ZjU4ZWI0MzUxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwibWFya2V0UHJpY2UiOjE1Ny4zLCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwicGF5bWVudE1ldGhvZERldGFpbCI6IiIsIm1zZyI6IiIsImFjY291bnRJbmZvIjoiIiwiZm9yVHJ1c3RlZCI6Im5vIiwidmVyaWZpZWRFbWFpbFJlcXVpcmVkIjoibm8iLCJyZXF1aXJlRmVlZGJhY2tTY29yZSI6MCwiZmlyc3RUaW1lTGltaXRBc3NldCI6MCwicGF5bWVudFdpbmRvd01pbnV0ZXMiOjYwLCJoaWRkZW4iOmZhbHNlLCJiYW5uZWQiOmZhbHNlLCJ2ZXJpZmllZCI6dHJ1ZSwiYWRkZWQiOiIyMDI0LTEwLTIyVDIzOjMxOjQ3LjM5M1oifQ==
-

@ 4ba8e86d:89d32de4
2024-10-22 23:20:59
Usar um gerenciador de senhas pode resolver vários problemas, incluindo a dificuldade de criar senhas fortes e únicas, o risco de reutilização de senhas e a possibilidade de comprometimento de contas devido a senhas fracas ou roubadas. Com o uso de um gerenciador de senhas, o usuário pode criar senhas fortes e únicas para cada conta, sem precisar se preocupar em lembrar de todas elas. Além disso,um gerenciador de senhas pode ajudar a simplificar o processo de login, economizando tempo e reduzindo a frustração.
O KeepassDX é uma versão do software de gerenciamento de senhas Keepass, desenvolvido originalmente por Dominik Reichl em 2003. O Keepass é um software gratuito e de código aberto para desktops, que permite que os usuários armazenem suas senhas em um banco de dados seguro, criptografado com algoritmos avançados. Em 2017, o desenvolvedor alemão Brian Pellmann criou o KeepassDX como uma versão para dispositivos móveis, com o objetivo de tornar mais fácil para os usuários gerenciarem suas senhas em smartphones e tablets.
O KeepassDX foi criado a partir do código-fonte do Keepass e foi projetado para ser fácil de usar, seguro e personalizável. Pellmann adicionou várias funcionalidades novas ao KeepassDX, incluindo a capacidade de importar senhas de outros gerenciadores de senhas, a organização de senhas em categorias e a compatibilidade com serviços de armazenamento em nuvem para sincronização entre dispositivos.
Algumas das funcionalidades do KeepassDX incluem a criação de senhas fortes e únicas, preenchimento automático de senhas, autenticação de dois fatores e organização de senhas por categorias. O KeepassDX também oferece uma ferramenta para importação de senhas de outros gerenciadores de senhas, o que torna a transição para o uso do KeepassDX mais fácil.
Passo a passo instalação do aplicativo KeepassDX:
1. Baixe e instale o KeepassDX em seu dispositivo móvel
https://play.google.com/store/apps/details?id=com.kunzisoft.keepass.free
2. Clique em [CRIAR NOVO BANCO DE DADOS]
3. Selecione o local do arquivo no meu caso é " transferência "
Semelhante ao KeePassXC, o KeePassDX suporta o formato de banco de dados .kbdx (por exemplo, Passwords.kdbx) para armazenar senhas de contas importantes. Você deve salvar este arquivo em um local de fácil acesso para você, mas difícil de encontrar para outras pessoas que você não deseja visualizar as informações. Em particular, evite salvar seu arquivo de banco de dados em um serviço de armazenamento online, conectado às suas contas, pois pode ser acessado por outras pessoas.
4. Digite um nome para seu banco de dados
Neste exemplo, " urso " nosso banco de dados como "urso.kdbx"; você pode escolher um nome de sua preferência. Você pode usar um nome que disfarce o arquivo e o torne menos óbvio para invasores que podem tentar acessar seu telefone e exigir que você desbloqueie o banco de dados.
Também é possível alterar a "extensão" no final do nome do arquivo. Por exemplo, você pode nomear o banco de dados de senhas "Revoltadeatlas.pdf" "primainterior.jpg " e o sistema operacional geralmente dará ao arquivo um ícone de "aparência normal". Lembre-se de que, se você der ao seu banco de dados de senhas um nome que não termine em ".kdbx", não poderá abrir o arquivo diretamente. Em vez disso, você terá que iniciar o KeePassDX primeiro e, em seguida, abrir seu banco de dados clicando no botão "Abrir banco de dados existente". Felizmente, o KeePassDX lembra o último banco de dados que você abriu, então você não terá que fazer isso com frequência.
https://github.com/Kunzisoft/KeePassDX
-

@ aa8de34f:a6ffe696
2024-10-22 19:36:06
##
Das Internet hat ein Problem. Nur wenige Leute wissen, dass dieses Problem existiert, aber hey, das liegt in der Natur ernsthafter, nicht offensichtlicher Probleme: Sie sind unsichtbar bis sie es nicht mehr sind. Das Problem mit dem Internet ist, dass Informationen frei sein wollen. Und wenn etwas FREI sein will wie in Freiheit, wird es mit genügend Zeit auch frei wie im Bier. Lass es mich erklären.
### Luftverschmutzung
Jeden Tag verbrauchen wir ungeheure Mengen an Daten. Jede Sekunde jeder Minute strömen Bits und Bytes durch die Reihe von Leitungen die wir alle kennen und lieben: das Internet. Wir nehmen es als selbstverständlich hin und die meisten von uns halten das derzeitige Monetarisierungsmodell – sowie alle damit einhergehenden Übel – ebenfalls für selbstverständlich. Wir halten nur selten inne und denken über die seltsame Welt der Bits und Bytes nach. Wie wunderbar das alles ist, aber auch wie fremd. Wie es unser Leben bereits verändert hat und wie es unsere Zukunft weiter verändern wird. Woher kommen die Nullen und Einsen? Wie funktioniert das alles? Und vor allem: Wer zahlt dafür? Die Bits und Bytes, die durch unsere Glasfaserkabel rasen, sind so unsichtbar wie die Luft die wir atmen. Das ist keine schlechte Metapher wenn ich so darüber nachdenke. Solange wir keine Atemprobleme haben, müssen wir nicht anhalten und jedes einzelne Molekül, das wir einatmen, untersuchen. Ebenso lange wir keine Schwierigkeiten haben digitale Inhalte zu erstellen und zu konsumieren, brauchen wir auch nicht innezuhalten und all die verschiedenen Teile zu untersuchen, die unsere Aufmerksamkeitsökonomie am Laufen halten.\
**Aufmerksamkeitsökonomie**. Was für eine treffende Beschreibung. Wie wir inzwischen alle wissen sollten, ist das was wir konsumieren nicht umsonst, sondern wir bezahlen teuer dafür: mit unserer Aufmerksamkeit unter anderem.
### Paying Attention – mit Aufmerksamkeit bezahlen
In der schnelllebigen Welt von heute muss man, um den Gewinn zu maximieren, die Aufmerksamkeit maximieren. Aber es ist eine eigentümliche, oberflächliche Art von Aufmerksamkeit. Es ist nicht die konzentrierte Art von Aufmerksamkeit, die tiefes Denken und sinnvolle Gespräche erfordern würden. Ich glaube, dass dies zumindest teilweise der Grund ist, warum viele Dinge so kaputt sind. Warum unser gesellschaftlicher Diskurs so zersplittert ist, unsere Politik so polarisiert, wir so gelähmt sind und unsere Analysen oft so oberflächlich sind wie unsere Wünsche.\
Die Aufmerksamkeitsökonomie hat uns fein säuberlich in Echokammern für persönliche Wahrheiten eingeteilt. Ironischerweise besteht die einzige Wahrheit die es wert ist, in der Aufmerksamkeitsökonomie verfolgt zu werden, darin, wie man eine maximale Anzahl von Menschen für eine maximale Zeitspanne maximal empört halten kann. Und das alles ohne dass die Teilnehmer merken, dass sie in einem selbst gewählten algorithmischen Gefängnis gefangen sind.
### Du bist das Produkt
Die Redewendung „Wenn etwas kostenlos ist, bist du das Produkt“ kann nicht oft genug wiederholt werden. Aus dem einen oder anderen Grund erwarten wir, dass die meisten Dinge Online „kostenlos“ sind. Natürlich gibt es so etwas wie ein kostenloses Mittagessen nicht – nichts ist umsonst. Bei Online-Diensten werden deine Daten gesammelt und an den Meistbietenden verkauft, der in der Regel eine Werbeagentur oder eine Regierungsbehörde ist. Oder beides.\
Alle Big-Data-Unternehmen spionieren dich nicht nur aus, sondern nutzen auch eine Vielzahl von dunklen Mustern und unethischen Praktiken, um aus deinen Interaktionen auch den letzten Tropfen an Daten herauszuholen. Ob es sich dabei um den Facebook-Pixel, Google Analytics oder etwas anderes handelt, spielt keine Rolle. Du wirst nachverfolgt, überwacht und katalogisiert. Was du siehst, wie lange, zu welchen Zeiten, wie häufig und was du als Nächstes sehen wirst, wird sorgfältig von einem gewinnmaximierenden Algorithmus orchestriert. Profit für die Plattform, nicht für dich. Natürlich geht es in der Regel darum, dass alle davon profitieren: Nutzer, Urheber, Werbetreibende und die Plattformen gleichermaßen. Das evolutionäre Umfeld, das durch diese Anreizstrukturen geschaffen wird, führt jedoch häufig dazu, dass seichte, aufmerksamkeitsstarke und sensationslüsterne Schnipsel ausgewählt werden. Zum Zeitpunkt dieses Schreibens – Block 716.025 – ist der Inbegriff eines solchen Umfelds TikTok, eine videobasierte Dopaminmaschine, die dir das filmische Äquivalent von Heroin gemischt mit Crack zeigt. Harte Drogen für den Verstand, maßgeschneidert für deine besonderen Vorlieben. Eine wahrhaft verfluchte App. Leider unterscheiden sich die meisten dieser Plattformen nur in der Größe, nicht in der Art.
### Zulässige Meinungen
„Es ist gar nicht so schlimm“, sagen wir uns. „Sieh dir all die nützlichen Informationen an!“, denken wir, während wir durch unsere Feeds scrollen, und füttern damit ungewollt die Maschine, die uns im Gegenzug mit Dopamin versorgt.\
Aber täuschen Sie sich nicht: Den verantwortlichen Unternehmen geht es nicht darum, uns mit nützlichen (oder wahrheitsgemäßen) Informationen zu versorgen. Es geht ihnen darum uns auszutricksen, damit wir die Maschine füttern.\
Wie könnte es anders sein? Man ist was man verfolgt, und man wird das worauf man optimiert wird. Aus Sicht der Plattform geht es um Klicks, nicht um Qualität. Auf den ersten Blick mag die Maximierung von Klicks und Verweildauer eine harmlose Sache sein. Schließlich muss man ja Geld verdienen um zu überleben. Es ist ja nur eine Anzeige. Wie schlimm kann es schon werden?\
Leider sind die Probleme, die damit einhergehen, zunächst unsichtbar. So wie Krebs für den Raucher unsichtbar ist, der gerade seine erste Zigarette geraucht hat, und Leberzirrhose für den Trinker unsichtbar ist, der gerade seinen ersten Drink zu sich genommen hat, so sind Deplatforming, Zensur, Polarisierung und Manipulation der öffentlichen Meinung für den Prosumenten unsichtbar, der gerade seine erste Anzeige auf einer geschlossenen Plattform gesehen hat. Wir können uns wahrscheinlich darauf einigen, dass wir das erste Inning (Stichwort Baseball) in dieser Frage hinter uns haben. Zensur ist die Norm, Deplatforming wird bejubelt, die Polarisierung ist auf einem Allzeithoch, und die öffentliche Meinung wird manuell und algorithmisch manipuliert wie nie zuvor.\
„Der Konsens ist, dass du zu dumm bist, um zu wissen was gut für dich ist und dass deine öffentliche Meinung zu unverschämt ist, um öffentlich geäußert zu werden. Schlimmer noch, es sollte gar nicht erst deine Meinung sein. Hier ist der Grund warum du falsch liegst. Hier ist eine Quelle die auf eine zulässige Meinung hinweist. Hier sind einige Experten, die mit uns übereinstimmen. Unsere intelligenten und hilfreichen Algorithmen haben die ganze Denkarbeit für dich erledigt, und sie liegen nie falsch. Genauso wenig wie die Experten.“\
Das ist die Welt, in der wir bereits leben. Es ist nicht erlaubt frei zu sprechen. Es ist nicht erlaubt frei zu denken. Du darfst dich nicht frei äußern. Dein Bild ist beleidigend und muss daher entfernt werden. Dein Meme ist zu nah an der Wahrheit oder zu kriminell lustig; deshalb müssen wir dich für ein oder zwei Wochen ins Twitter-Gefängnis stecken. Du sagst etwas mit dem wir nicht einverstanden sind; deshalb müssen wir dich auf Lebenszeit sperren – auch wenn du ein amtierender Präsident bist, wohlgemerkt. Du hast in einem Video das falsche Wort gesagt oder ein urheberrechtlich geschütztes Lied im Hintergrund abgespielt; deshalb müssen wir dir dein Einkommen wegnehmen. Du hast ein Bild von dir ohne Maske gepostet; deshalb müssen wir dich verbieten und den Behörden melden.1\
Die Tatsache, dass der obige Satz nicht mehr nur im Bereich der dystopischen Science-Fiction angesiedelt ist, sollte jeden beunruhigen. Aus dem Cyberspace entfernt – weil ich frei atmen wollte. Seltsame Zeiten.
### Evolutionärer Druck
Wie ist es dazu gekommen? Wenn ich gezwungen wäre, eine kurze Antwort zu geben, würde ich Folgendes sagen: Wir sind von Protokollen zu Plattformen übergegangen, und Plattformen sind nur so gut wie ihre Anreize.\
Die Anreizstruktur der Plattformen, auf denen wir leben, ist die evolutionäre Umgebung, die das Überleben diktiert. Alles, was überleben will, muss sich daran orientieren. Das gilt natürlich für alle Bereiche der Wirtschaft. Nimm zum Beispiel Printmagazine. Wenn deine Zeitschrift kein schönes weibliches Gesicht auf der Titelseite hat, wird sie aus sehr menschlichen evolutionären Gründen nicht so oft gekauft werden wie die Zeitschriften, die ein solches Gesicht haben. Sie kann sich also nicht selbst reproduzieren und wird folglich sterben. Ähnlich verhält es sich mit einem Online-Nachrichtenportal, wenn es keine ausreichenden Werbeeinnahmen generiert und nicht in der Lage ist sich zu reproduzieren, wird es sterben. Aus diesem Grund hat jede Zeitschrift ein schönes weibliches Gesicht auf dem Cover. Und das ist der Grund, warum jede werbefinanzierte Online-Nachrichtenquelle zu Clickbait verkommt.
<img src="https://cdn.satellite.earth/856054a1932c9fb70f9ae85bcb6d2d47330babb3cf7ac606c7861a09c8597f61.webp">
#### Eines dieser Gesichter ist anders als die anderen
Das ist auch der Grund, warum sich Feed-basierte Empfehlungsmaschinen in Spielautomaten für deine Dopaminrezeptoren verwandeln. Je länger du an deinem Bildschirm klebst, desto mehr Werbung siehst du, desto mehr Einnahmen werden für die Plattform generiert. Das ist auch der Grund, warum die meisten YouTube-Kanäle zu 7- bis 15-minütigen Kurzvideos mit Vorschaubildern verkommen, die das Gesicht von jemandem zeigen, der gerade auf ein Legostück getreten ist. Kurz genug, um dich zu überzeugen es anzusehen, lang genug, um dich vergessen zu lassen, welches Video du dir eigentlich ansehen wolltest. Wie Ratten, die in hyperpersonalisierten Skinner-Boxen auf Knöpfe drücken, werden wir in Suchtzyklen konditioniert, um die Gewinne der Aktionäre zu maximieren.
### Profitmaximierung
Plattformen sind Unternehmen und für Unternehmen gibt es Anreize die Gewinne der Aktionäre zu maximieren. Gegen Gewinne ist nichts einzuwenden und gegen Aktionäre ist auch nichts einzuwenden. Ich glaube jedoch, dass die Informationsrevolution, in der wir uns befinden, die evolutionäre Landschaft in zwei Teile gespalten hat. Nennen wir diese Landschaften „breit“ und „schmal“.\
Um die Gewinne durch breit angelegte Werbung zu maximieren, müssen Kontroversen und extreme Meinungen auf ein Minimum reduziert werden. Indem man den kleinsten gemeinsamen Nenner anspricht, kommen Politik und Zensur sofort ins Spiel. Umgekehrt müssen Kontroversen und extreme Meinungen maximiert werden, wenn die Gewinne durch schmale, gezielte Werbung erzielt werden sollen. Allein dadurch, dass verschiedenen Untergruppen unterschiedliche Informationen gezeigt werden, werden Polarisierung und Fragmentierung kontinuierlich verstärkt.
<img src="https://cdn.satellite.earth/0d3a88d2700a3c26ed049b09d512a9a35dfc390bc95151e29d6950972114a00e.webp">
Allgemeine Kohäsion vs. algorithmische Spaltung
Diese beiden Extreme sind zwei Seiten der gleichen Medaille. Es mag den Anschein haben, als ginge es um Kabelfernsehen gegen den algorithmischen Newsfeed, aber in Wirklichkeit handelt es sich um zwei unterschiedliche Ansätze, die dasselbe Ziel verfolgen: möglichst viele Menschen vor dem Bildschirm zu halten, damit sie mehr Werbung sehen. Das erste ist ein Beruhigungsmittel, das zweite ein Stimulans.\
Zugegeben, die obige Charakterisierung mag übertrieben sein, aber das Problem bleibt bestehen: Wenn wir nicht direkt für etwas bezahlen, bezahlen wir es indirekt, auf die eine oder andere Weise. Immer.
Der Punkt ist der folgende: Plattformen für freie Meinungsäußerung können nicht existieren. Es kann nur Protokolle der freien Meinungsäußerung geben. Wenn jemand kontrollieren kann, was gesagt wird, wird jemand kontrollieren, was gesagt wird. Wenn du Inhalte überwachen, filtern und zensieren kannst, wirst du Inhalte überwachen, filtern und zensieren.
Alle Plattformen werden mit diesem Problem konfrontiert, ganz gleich wie makellos ihre Absichten sind. Selbst wenn du dich anfangs als Plattform für freie Meinungsäußerung positionierst, wirst du auf lange Sicht gezwungen sein, einzugreifen und zu zensieren. Letztendlich wenn du für Inhalte, die du hostest oder übermittelst, vom Staat haftbar gemacht werden kannst, wirst du auch für Inhalte, die du hostest oder übermittelst, vom Staat haftbar gemacht werden.
### Selbstzensur
Doch lange bevor die staatliche Zensur ihr hässliches Haupt erhebt, wird die abschreckende Wirkung der Selbstzensur zu spüren sein. Wenn andere wegen der Äußerung bestimmter Meinungen enttabuisiert und dämonisiert werden, werden die meisten Menschen sehr vorsichtig sein, diese Meinungen zu äußern. Bewusst und unbewusst bringen wir uns selbst langsam zum Schweigen.
Wenn es um Selbstzensur geht, spielt auch die Werbung eine Rolle. Schließlich würdest du nicht die Hand beißen, die dich füttert, oder? Im schlimmsten Fall sagen dir die Werbetreibenden und Führungskräfte, was gesagt werden darf und was nicht. Sie werden dir sagen, welche Meinungen innerhalb und welche außerhalb des Overton-Fensters liegen. Und wenn sie es nicht tun, wirst du eine fundierte Vermutung anstellen und deine Aussagen entsprechend anpassen.
### Ein Problem und ein Paradoxon
Zurück zum ursprünglichen Problem: Warum können wir Informationen nicht wie eine normale Ware verkaufen? Warum führt der einfache Ansatz – Inhalte hinter eine Bezahlschranke zu stellen – zu so schlechten Ergebnissen? Ich glaube, es gibt zwei Gründe, die ich das „MTX-Problem“ und das „DRM-Paradoxon“ nennen möchte.
Das MTX-Problem, wobei MTX die Abkürzung für „mentale Transaktion“ (mental transaction) ist, bezieht sich auf das Problem der nicht reduzierbaren mentalen Transaktionskosten, die jeder Transaktion innewohnen. Jedes Mal, wenn du auf eine Bezahlschranke stößt, musst du eine bewusste Entscheidung treffen: „Möchte ich dafür bezahlen?“
Wie Szabo überzeugend darlegt, lautet die Antwort in den meisten Fällen, insbesondere wenn die Kosten gering sind, nein. Dafür gibt es keine technischen Gründe, sondern psychologische Gründe. Es stellt sich heraus, dass die Mühe, herauszufinden, ob sich diese Transaktion lohnt oder nicht – ein Prozess, der in deinem Kopf stattfindet – einfach zu groß ist. Wenn man über einen Mikrokauf nachdenken muss, sinkt die Wahrscheinlichkeit, dass man diesen Kauf tätigt, drastisch. Deshalb sind Flatrates und Abonnements der Renner: Man muss nur einmal darüber nachdenken.
Bei den kleinsten Mikrotransaktionen ist dies sogar aus rein wirtschaftlicher Sicht der Fall. Wenn man einen Stundenlohn von 20 USD zugrunde legt und zwei Sekunden lang darüber nachdenkt: „Ist das 21 Sats wert?“, kostet das etwas mehr als 1¢, also mehr als der Preis der betreffenden Mikrotransaktion.\[2\] Das ist sowohl psychologisch als auch wirtschaftlich nicht machbar. Dies ist, kurz gesagt, das MTX-Problem.
Aber das ist nicht das einzige Problem, das die Monetarisierung digitaler Inhalte belastet. Wie bereits erwähnt, gibt es auch das DRM-Paradoxon. DRM, kurz für „Digital-Rechte Management“ (Digital Rights Management), ist ein vergeblicher Versuch, das Kopieren von Informationen zu verhindern. Es sollte sich von selbst verstehen, dass nicht kopierbare Informationen ein Oxymoron sind, aber im Zeitalter von NFTs und vielem anderen Unsinn muss das leider ausdrücklich gesagt werden. Lass es mich also für dich buchstabieren: Man kann keine Informationen erstellen, die nicht kopiert werden können. Punkt. Oder, um es mit den Worten von Bruce Schneier zu sagen: „Der Versuch, digitale Dateien unkopierbar zu machen, ist wie der Versuch, Wasser nicht nass zu machen.“
Es liegt in der Natur der Sache, dass Informationen, wenn sie gelesen werden können, auch kopiert werden können – und zwar mit perfekter Genauigkeit. Kein noch so großer Trick oder künstliche Beschränkungen werden diese Tatsache ändern. Aus diesem Grund werden digitale Artefakte wie Filme und Musik immer kostenlos erhältlich sein. Es ist trivial für jemanden der Zugang zu diesen Artefakten hat, diese zu kopieren – zu Grenzkosten von nahezu Null, wohlgemerkt – und sie anderen zugänglich zu machen. Mit genügend Zeit und Popularität wird also jeder Film, jedes Lied und jedes Dokument für die\
Allgemeinheit kostenlos verfügbar sein. Die Natur der Information lässt kein anderes Ergebnis zu. Daher das Sprichwort: Information will frei sein.
Obwohl der Versuch etwas zu schaffen das es nicht geben kann – Informationen die nicht kopiert werden können – an sich schon paradox ist, meine ich damit nicht das DRM-Paradoxon. Was ich meine, ist etwas viel Lustigeres. Es ist wiederum psychologischer, nicht technischer Natur. Das Paradoxon ist folgendes: Inhalte werden nur dann hinter einer Bezahlschranke bleiben, wenn sie schlecht sind. Wenn sie gut sind, wird sie jemand freilassen.
Wir alle kennen das. Wenn ein Artikel tatsächlich lesenswert ist, wird jemand, der sich hinter der Bezahlschranke befindet, einen Screenshot davon machen und ihn in den sozialen Medien veröffentlichen. Wenn der Film es wert ist angeschaut zu werden, wird er auf verschiedenen Websites verfügbar sein, die Piratenschiffe als ihre Logos haben. Wenn der Song es wert ist gehört zu werden, wird er auf Streaming-Seiten kostenlos zur Verfügung stehen. Nur die schrecklichen Artikel, die obskursten Filme und die Lieder, bei denen einem die Ohren bluten, bleiben hinter Bezahlschranken.
Daraus ergibt sich das Paradoxon: Inhalte bleiben nur dann hinter Bezahlschranken, wenn sie schlecht sind. Wenn sie gut sind, werden sie freigelassen.
Ich persönlich glaube, dass das MTX-Problem ein größeres Problem darstellt als das DRM-Paradoxon. Die traditionelle Lösung für das MTX-Problem ist das Abonnementmodell, wie bei Netflix, Spotify, Amazon und so weiter. Das DRM-Paradoxon bleibt bestehen, aber es stellt sich heraus, dass dies kein Problem ist wenn man den „legitimen“ Zugang zu Informationen bequem genug gestaltet. Die Opportunitätskosten für das Herunterladen, Speichern, Pflegen und Warten einer privaten Liedersammlung sind für die meisten Menschen einfach zu hoch. Die bequemere Lösung ist für das verdammte Spotify-Abo zu bezahlen. Allerdings können wir bereits eines der Probleme erkennen, die mit dem Abonnementmodell verbunden sind. Der folgende Comic beschreibt es gut:
Comic von /u/Hoppy_Doodle
Die Verbreitung von Streaming-Plattformen zwingt dich dazu, ein Netflix-Abonnement, ein Amazon-Prime-Abonnement, ein Hulu-Abonnement, ein Disney-Plus-Abonnement, ein YouTube-Premium-Abonnement und so weiter abzuschließen. Und das war nur das Videostreaming. Den gleichen Abo-Zoo gibt es für Musik, Bücher, Spiele, Newsletter, Blogbeiträge usw.
Und was ist die Lösung?
### Akzeptiere die Natur von Informationen
Die Lösung beginnt mit Akzeptanz. Der Verkauf digitaler Inhalte auf herkömmliche, transaktionale Weise funktioniert nicht oder zumindest nicht sehr gut. Eine Transaktion mit einem digitalen Foto eines Apfels ist etwas ganz anderes als eine Transaktion mit einem physischen Apfel.
George Bernard Shaw hat es am besten gesagt: „Wenn du einen Apfel hast und ich habe einen Apfel und wir tauschen diese Äpfel, dann haben wir beide immer noch jeweils einen Apfel. Aber wenn Sie eine Idee haben und ich eine Idee habe und wir diese Ideen austauschen, dann hat jeder von uns zwei Ideen.“ Da sich digitale Informationen wie eine Idee verhalten, gibt es keinen Grund, sie künstlich zu verknappen. Das gilt nicht nur in philosophischer, sondern auch technischer Hinsicht. Computer sind Kopiermaschinen. Das war schon immer so und wird auch so bleiben. Die einzige Möglichkeit, Informationen von einer Maschine auf eine andere zu übertragen, besteht darin, sie zu kopieren. Dies allein sollte die Sinnlosigkeit der Behandlung von Informationen als physische Objekte offenkundig machen.
Wenn es um die Monetarisierung von Informationen im offenen Web geht, müssen wir unsere Denkweise mit der Natur der Information in Einklang bringen. Wie oben beschrieben, sind Informationen nicht knapp, leicht zu kopieren, leicht zu verändern und wollen frei sein. Ich glaube, dass das richtige Monetarisierungsmodell diese Werte respektieren und ähnliche Eigenschaften haben muss. Es muss offen, transparent, erweiterbar und nicht zuletzt völlig freiwillig sein.
Dieses Modell hat einen Namen: Value-for-Value.
### Wiederbeleben der Straßenmusik
Die Idee ist einfach, klingt aber radikal: Du stellst deine Inhalte kostenlos zur Verfügung, für jeden, ohne Zugangsbeschränkungen. Wenn die Menschen Spaß daran haben, wenn sie einen Nutzen daraus ziehen, dann machst du es den Menschen leicht etwas zurückzugeben.\
Es mag in der heutigen Zeit ungeheuerlich klingen, aber dieses Modell funktioniert seit Tausenden von Jahren. Es ist das Modell der Straßenkünstler, das Modell der Straßenmusikanten, das Modell des freiwilligen Gebens. Im Cyberspace stoßen wir jedoch nicht an die physischen Grenzen der traditionellen Straßenmusikanten. Digitale Inhalte lassen sich auf eine Art und Weise skalieren, wie es bei Darbietungen in der realen Welt nie der Fall sein wird.
Das Value-for Value-Modell stellt das traditionelle Zahlungsmodell auf den Kopf. Traditionell folgt der Genuss der Bezahlung. Beim Value-for-Value-Ansatz folgt die Zahlung dem Genuss – freiwillig. Es steht dir frei, dem Straßenmusiker zuzuhören und weiterzugehen, aber – und das ist etwas was das Publikum intuitiv weiß – wenn du willst, dass die Musik weitergeht, solltest du ein paar Münzen in den Hut werfen.
[Give value back](https://ts.dergigi.com/api/v1/invoices?storeId=3WkiYEG5DaQv7Ak5M2UjUi1pe5FFTPyNF1yAE9CVLNJn&orderId=V4V-busking&checkoutDesc=Value+for+Value%3A+Give+as+much+as+it+is+worth+to+you.¤cy=USD)
Das Schöne an diesem Modell ist, dass es die Anreize neu ausrichtet. Man versucht nicht, die Klicks, die Verweildauer oder irgendeine andere der unzähligen Kennzahlen zu maximieren. Man will dem Publikum einen Mehrwert bieten, und das ist alles. Und wenn das Publikum einen Nutzen daraus gezogen hat, wird ein gewisser Prozentsatz etwas zurückgeben. Alles, was man tun muss, ist zu fragen.
### Eine wertvolle Alternative
Wir stehen erst am Anfang dieses monumentalen Wandels. Ich hoffe, dass sich das Modell „Value for Value“ weiterhin als praktikable Alternative zu Werbung, Zensur, Deplatforming und Demonetisierung durchsetzen wird.
Das Value-for-Value-Modell nimmt das „sie“ aus der Gleichung heraus. Sie filtern, sie zensieren, sie demonetisieren, sie deplatformieren. Es spielt nicht einmal eine Rolle, wer „sie“ sind. Wenn es „sie“ gibt, werden sie einen Weg finden, es zu versauen.
Value-for-Value beseitigt „sie“ und überträgt dir die Verantwortung. Du bist der Herrscher im Reich des Einen, allein verantwortlich für deine Gedanken und deine Sprache. Wenn wir Befreiung (und Erlösung) im Cyberspace wollen, müssen wir dem Einzelnen wieder die Verantwortung übertragen. Wie immer gilt: Freiheit und Unabhängigkeit erfordern Verantwortung.
In der besten aller Welten gibt es für die Schöpfer einen Anreiz, nichts anderes zu tun als zu erschaffen. Man bedient nur sich selbst und diejenigen, die an den Werken interessiert sind. Keine Mittelsmänner. Direkt, von Mensch zu Mensch, Value-for-Value.
### Was uns erwartet
Zugegeben, heute ist es nicht gerade einfach, seine Infrastruktur selbst zu hosten. Es ist einschüchternd, einen eigenen Knotenpunkt (Node) zu betreiben, um Zahlungen auf selbständige Weise zu erhalten. Aber es wird nicht nur einfacher, es wird zunehmend notwendig.
Wir müssen nicht nur alles einfacher machen, sondern uns auch des oben beschriebenen MTX-Problems bewusst sein. Jeder Schritt, der es schafft, die mentalen Transaktionskosten im Ökosystem der Wertschöpfung zu reduzieren, ist ein Schritt in die richtige Richtung.
Die Wertfunktion von Podcasting 2.0 ist ein solcher Schritt. Sie ermöglicht und automatisiert Zahlungen im Minutentakt, ohne dass der Nutzer zusätzlich eingreifen muss. Sobald du eingerichtet bist, wird deine Geldbörse automatisch Zahlungen vornehmen. Ich glaube, dass weitere Iterationen dieser Idee in alle Medientypen integriert werden können, sei es Audio, Video, Bilder, das geschriebene Wort, und so weiter. Ich glaube, dass wir kurz vor der Protokollversion von Patreon stehen: alle Vorteile der Reduzierung der mentalen Transaktionskosten auf Null, ohne die Reibung und die Zensur, die einer plattformbasierten Lösung innewohnen. Ob es in Form von BOLT12 wiederkehrenden Zahlungen oder etwas ganz anderem kommen wird, bleibt abzuwarten. Ich bin jedoch zuversichtlich, dass dies zu gegebener Zeit der Fall sein wird.
### Schlussfolgerung
Nicht nur unser Papiergeld ist kaputt, auch das Monetarisierungsmodell des Internets ist kaputt. Die werbebasierten Plattformen der heutigen Zeit sind auf Engagement durch Spaltung und Polarisierung optimiert und nutzen dunkle Muster und Sucht. Es wird nicht einfach sein, aus den Zwangsschleifen auszubrechen, die für uns eingerichtet wurden, aber dank des selbstverwalteten Tech-Stacks, der derzeit entsteht, gibt es eine praktikable Alternative: das Value-for-Value-Modell.
Das „Straßenmusiker“-Monetarisierungsmodell (busking monetization model) hat in der Vergangenheit viele Jahrhunderte lang funktioniert, und dank Bitcoin und dem Lightning Network bin ich zuversichtlich, dass es auch in der Zukunft noch Jahrhunderte lang funktionieren wird. Wir sind fast am Ziel. Wir müssen nur noch herausfinden, wie wir den Hut richtig auf dem Boden positionieren und wo die besten Plätze in der Stadt sind, um sozusagen aufzutreten.
Value-for-Value löst das DRM-Paradoxon in seiner Gesamtheit und wird – mit dem richtigen Maß an Automatisierung und vernünftigen Vorgaben – auch das MTX-Problem lösen. Wenn wir das richtig hinbekommen, können wir uns vielleicht aus dem evolutionären Überlebenskampf der Plattformen befreien und uns in das quasi unsterbliche Reich der Protokolle begeben.
Es gibt viel zu erforschen, viele Werkzeuge zu entwickeln und viele vorgefasste Meinungen zu zerstören. Direkt vor unseren Augen vollzieht sich ein seismischer Wandel, und ich freue mich darauf, mit euch allen auf den Wellen zu reiten. Vorwärts marsch!
---
*Dies ist ein übersetzter Gastbeitrag von Gigi aus seinem [Blog](https://dergigi.com/). Die geäußerten Meinungen sind ausschließlich seine eigenen und spiegeln nicht notwendigerweise die des Re-Publishers oder Aprycot Media wider. Quelle: https://aprycot.media/blog/freiheit-der-werte/#*
-

@ eac63075:b4988b48
2024-10-21 08:11:11
Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
### **Sections:**
- **Introduction**
- **What Is Chat Control?**
- **Why Is the EU Pushing for Chat Control?**
- **The Privacy Concerns and Risks**
- **The Technical Debate: Encryption and Backdoors**
- **Global Reactions and the Debate in Europe**
- **Possible Consequences for Messaging Services**
- **What Happens Next? The Future of Chat Control**
- **Conclusion**
---
### **What Is Chat Control?**
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
#### **Origins of the Proposal**
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
#### **How Messaging Services Work**
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.
<img src="https://blossom.primal.net/31ace3b729fb9f6b4de286686f31a71db6dd7e3a363f868e1255a6f287eb0b94.png">
#### **Key Elements of Chat Control**
- **Automated Content Scanning**: Service providers would use algorithms to scan messages for illegal content.
- **Circumvention of Encryption**: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- **Mandatory Reporting**: If illegal content is detected, providers would be required to report it to authorities.
- **Broad Applicability**: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
#### **Why It Matters**
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
---
### **Why Is the EU Pushing for Chat Control?**
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
#### **Protecting Children and Preventing Crime**
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
#### **Legal Context and Legislative Drivers**
The push for Chat Control is rooted in several legislative initiatives:
- **ePrivacy Directive**: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
- **Temporary Derogation**: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
- **Regulation Proposals**: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
#### **Balancing Security and Privacy**
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
- **Targeted Scanning**: Focusing on specific threats rather than broad, indiscriminate monitoring.
- **Judicial Oversight**: Requiring court orders or oversight for accessing private communications.
- **Data Protection Safeguards**: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.
<img src="https://blossom.primal.net/9533aedc9f83564d53633eac1a6d431d1e311028a478dd4b7f3a59b2c449e95a.png">
#### **The Urgency Behind the Push**
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
#### **Criticism and Controversy**
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
---
### **The Privacy Concerns and Risks**
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
#### **Infringement on Privacy Rights**
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
#### **Erosion of End-to-End Encryption**
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
#### **Concerns from Privacy Advocates**
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- **Security Risks**: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- **Global Implications**: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- **Ineffectiveness Against Crime**: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.
<img src="https://blossom.primal.net/51722887ebf55c827cc20bcfade3ea9b3628265b7fa3547504b2fff45f34f175.png">
#### **Potential for Government Overreach**
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
#### **Real-World Implications for Users**
- **False Positives**: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- **Chilling Effect**: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- **Data Misuse**: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
#### **Legal and Ethical Concerns**
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- **Violation of Fundamental Rights**: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- **Questionable Effectiveness**: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
#### **Opposition from Member States and Organizations**
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
---
### **The Technical Debate: Encryption and Backdoors**
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
#### **What Is End-to-End Encryption (E2EE)?**
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- **Security Assurance**: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- **Widespread Use**: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
#### **How Chat Control Affects Encryption**
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- **Introduce Backdoors**: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- **Client-Side Scanning**: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
#### **The Risks of Weakening Encryption**
**1. Compromised Security for All Users**
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- **Exploitable Gaps**: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- **Universal Impact**: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
**2. Undermining Trust in Digital Services**
- **User Confidence**: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- **Business Implications**: Companies relying on secure communications might face increased risks, affecting economic activities.
**3. Ineffectiveness Against Skilled Adversaries**
- **Alternative Methods**: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- **False Sense of Security**: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
#### **Signal’s Response and Stance**
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- **Refusal to Weaken Encryption**: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- **Advocacy for Privacy**: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
#### **Understanding Backdoors**
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- **Security Vulnerabilities**: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- **Ethical Concerns**: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.
<img src="https://blossom.primal.net/67f45fd79ccdb7e2e2ecdc56297207dc0d1d073acb216857b6165b3bf9906997.png">
#### **The Slippery Slope Argument**
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- **Expanded Surveillance**: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- **Erosion of Rights**: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
#### **Potential Technological Alternatives**
Some suggest that it's possible to fight illegal content without undermining encryption:
- **Metadata Analysis**: Focusing on patterns of communication rather than content.
- **Enhanced Reporting Mechanisms**: Encouraging users to report illegal content voluntarily.
- **Investing in Law Enforcement Capabilities**: Strengthening traditional investigative methods without compromising digital security.
####
The technical community largely agrees that weakening encryption is not the solution:
- **Consensus on Security**: Strong encryption is essential for the safety and privacy of all internet users.
- **Call for Dialogue**: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
---
### **Global Reactions and the Debate in Europe**
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
#### **Support for Chat Control**
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- **Enhanced Security**: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- **Responsibility of Service Providers**: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- **Public Safety Priorities**: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
#### **Opposition within the EU**
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
**Germany**
- **Stance**: Germany has been one of the most vocal opponents of the proposed measures.
- **Reasons**:
- **Constitutional Concerns**: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- **Security Risks**: Weakening encryption is seen as a threat to cybersecurity.
- **Legal Challenges**: Potential conflicts with national laws protecting personal data and communication secrecy.
**Netherlands**
- **Recent Developments**: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- **Arguments**:
- **Effectiveness Doubts**: Skepticism about the actual effectiveness of the measures in combating crime.
- **Negative Impact on Privacy**: Concerns about mass surveillance and the infringement of citizens' rights.
Table reference: Patrick Breyer - Chat Control in 23 September 2024
#### **Privacy Advocacy Groups**
**European Digital Rights (EDRi)**
- **Role**: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- **Position**:
- **Strong Opposition**: EDRi argues that Chat Control is incompatible with fundamental rights.
- **Awareness Campaigns**: Engaging in public campaigns to inform citizens about the potential risks.
- **Policy Engagement**: Lobbying policymakers to consider alternative approaches that respect privacy.
**Politicians and Activists**
**Patrick Breyer**
- **Background**: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- **Actions**:
- **Advocacy**: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- **Public Outreach**: Using social media and public events to raise awareness.
- **Legal Expertise**: Highlighting the legal inconsistencies and potential violations of EU law.
#### **Global Reactions**
**International Organizations**
- **Human Rights Watch and Amnesty International**: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
**Technology Companies**
- **Global Tech Firms**: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- **Industry Associations**: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.
<img src="https://blossom.primal.net/e761aa2dd240a1a2e7d943565ccbda427b5a8054bf4e6e17c946711ab6370d5d.png">
#### **The Broader Debate**
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- **Legal Precedents**: How the EU's decision might influence laws and regulations in other countries.
- **Digital Sovereignty**: The desire of nations to control digital spaces within their borders.
- **Civil Liberties**: The importance of protecting freedoms in the face of technological advancements.
#### **Public Opinion**
- **Diverse Views**: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- **Awareness Levels**: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
####
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
---
### **Possible Consequences for Messaging Services**
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
#### **Impact on Encrypted Messaging Services**
**Signal and Similar Platforms**
- **Compliance Challenges**: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
- **Operational Decisions**: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
#### **Potential Blocking or Limiting of Services**
- **Regulatory Enforcement**: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
- **Access Restrictions**: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
#### **Effects on Smaller Providers**
- **Resource Constraints**: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
- **Innovation Stifling**: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.
<img src="https://blossom.primal.net/60a9cad69b45cc3ded1d1759312e49a57b3aa997db62e36016f40642943be5e9.png">
#### **User Experience and Trust**
- **Privacy Concerns**: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
- **Migration to Unregulated Platforms**: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
#### **Technical and Security Implications**
- **Increased Vulnerabilities**: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
- **Global Security Risks**: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
#### **Impact on Businesses and Professional Communications**
- **Confidentiality Issues**: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
- **Compliance Complexity**: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
#### **Economic Consequences**
- **Market Fragmentation**: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
- **Loss of Revenue**: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
#### **Responses from Service Providers**
- **Legal Challenges**: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
- **Policy Advocacy**: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
#### **Possible Adaptations**
- **Technological Innovation**: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
- **Transparency Measures**: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
####
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
---
### **What Happens Next? The Future of Chat Control**
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
#### **Current Status of Legislation**
- **Ongoing Negotiations**: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
- **Timeline**: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
#### **Key Influencing Factors**
**1. Legal Challenges and Compliance with EU Law**
- **Fundamental Rights Assessment**: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
- **Court Scrutiny**: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
**2. Technological Feasibility**
- **Development of Privacy-Preserving Technologies**: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
- **Implementation Challenges**: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
**3. Political Dynamics**
- **Member State Positions**: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
- **Public Opinion and Advocacy**: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
**4. Industry Responses**
- **Negotiations with Service Providers**: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
- **Potential for Self-Regulation**: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
#### **Possible Scenarios**
**Optimistic Outcome:**
- **Balanced Regulation**: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
**Pessimistic Outcome:**
- **Adoption of Strict Measures**: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
**Middle Ground:**
- **Incremental Implementation**: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
#### **How to Stay Informed and Protect Your Privacy**
- **Follow Reputable Sources**: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
- **Engage in the Dialogue**: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
- **Utilize Secure Practices**: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.
<img src="https://blossom.primal.net/1e2c0cd70d88629c54ac84f928ab107f08f698d2c7f0df511277fb44c1480f0a.png">
#### **The Global Perspective**
- **International Implications**: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
- **Collaboration Opportunities**: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
#### **Looking Ahead**
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
---
### **Conclusion**
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- **Erosion of Trust**: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- **Security Vulnerabilities**: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- **Stifling Innovation**: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- **Global Implications**: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.
<img src="https://blossom.primal.net/d3f07d8bc7a49ac291f14eb449879462c76ae407abbe728ddc6f93e11fabe11d.png">
---
Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
## Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-

@ fd208ee8:0fd927c1
2024-10-20 18:19:48
(Please note that this is not official financial or business advice, but rather a description of something we have done, on an informal basis.)
# A long, long time ago
It's been nearly a year, since nostr:nprofile1qydhwumn8ghj7argv4nx7un9wd6zumn0wd68yvfwvdhk6tcpypmhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjj7qpqs3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqv5atj2 came into being, mostly as a lark, involving a couple of members of our private chat group. Our initial plan was to work toward bounties, but Nostr bounties are a bit of a biased, uncertain thing, and our enthusiasm for that quickly waned.
So, what to do? Here we are, we three (nostr:npub1ecdlntvjzexlyfale2egzvvncc8tgqsaxkl5hw7xlgjv2cxs705s9qs735, nostr:npub1wqfzz2p880wq0tumuae9lfwyhs8uz35xd0kr34zrvrwyh3kvrzuskcqsyn, and I): IT professionals with little time, but plenty of intellectual energy, a Slack chat, a [GitHub repo](https://github.com/ShadowySupercode), and lots of frustration with the Nostr status quo.
We were, you see, Nostr end-users. We loved the idea of the protocol, but we were being regularly stymied by the poor quality of many implementations.
* Why can I not login? Oh, they fixed the login! Nope, still can't login.
* If I press this button, it says it sent, but it didn't send. Where note?
* They announced a new feature, but I tried it and it didn't work. Oh well.
* I noticed a bug in the client, reported it, and the issue is just rotting away in the project repo. Ignored.
* The website/relay/repo was here... yesterday. Today it has disappeared, and taken my zaps with it.
It was enough to make us want to tear our hair out. We decided that what Nostr needed... what it _really_ needed... was a **Nostr Stable Version**. Nothing glamorous. Nothing exotic. Nothing busy or excitable. Just something that stayed where you initially found it, ran, and actually worked. Something where you could report a bug and receive a prompt response. Maybe even something, where you could pay a reasonable fee and be _allowed to have expectations_ of some particular service being returned. And who better to build such a version, than people who want to use it, themselves?
# Things working is an underrated concept
I know that the very idea of software _running as expected_ and websites not appearing and disappearing suddenly, based upon what some particular developer had for lunch, tends to be met with little but scorn, from hardened, seasoned Nostriches (who are convinced that bugs are _all_ features), but I think the majority of potential users would see it differently.
I'm with the majority, on this one.
I like to click "save" buttons and have them save. If I publish something, I want it to appear under my list of published somethings. I like to type in the website address I always type in, and have it magically appear on my screen, as if there were a little man sitting at controls in my laptop, just waiting for me to write H-T-T-P-S... and then jump to attention.
My unreasonable expectations have no bounds, it is true. But unreasonable people are also people, so we would also like to have our own unreasonable things to play with. Scorn away. My save button will save, and my published something will publish, and my website will load _every damn time_, just to spite you.
In the larger scheme of things, you see, we win even if we fail, if we at least increase the competition enough, that _things working_ becomes the new standard. We can simply prove, definitively, that it is possible for Nostr things to work, if they are built by people who care if they work. If we also have fun together, learn something new, and come up with some cool, novel use cases, then that's pure profit.
We can only win, at this endeavor.
# Where to start?
## Name that brand
So, we had a team, we had a business idea, and we had a heck of a lot of motivation. What we didn't have, is a name. (Never underestimate the importance of naming things.)
We decided to name ourselves "GitCitadel" because "git" sounds techy, hints at our GitRepublic project, and is reminiscent of open-source development, and "citadel" reminds us of Bitcoin. The republic is at home in the citadel, naturally. All other products also live in the same citadel, hence the naming-convention of prefacing everything with "GC" (i.e. "GC Alexandria", "GC Sybil", "GC Aedile", etc.).
## Brand yourself
The next thing we did, was rent a domain and run a webserver on it. This is an important step because it gives you an Internet presence, allows you to have company NIP-05 and email addresses (a form of promotion), and it's simply exciting to have one. Feels so much more "official" and it helps increase the name-recognition of your company.
## Define yourself
We then sat down, together, over the Internet, and figured out who we are. Not who we individually are, but who we are, as a company. A company, after all, (according to the Cambridge Dictionary) is "an organization that produces or sells goods or services in order to make a profit". Now, a company's profits don't have to be monetary, but they should be something tangible. A company, in other words, is a team of people working toward some defined goal.
What is our goal? Well, we decided to think it over, sat down with the newer additions to the company (you can see who they are, on our [project wiki page](https://wikistr.com/gitcitadel-project), and came up with a Vision and a Mission:
The _vision_ is what the overall goals of the company are, whereas the _mission_ describes how those goals shall be achieved. Now, this is a sort of lofty, abstract statement, so it was important that we posted it someplace publicly (to keep ourselves accountable) and look at it regularly, so that we can ponder it and realign whatever we are currently working on, with this statement. We know the statement is well-designed, if considering it helps us make decisions about what to do next.
## Pay yourselves
(I'm going to switch from "we" to "you", here, as it's easier to write this part, but let's just pretend I didn't.)
The next thing on the list, is to arrange the finances, usually by setting up a Geyserfund, with an associated wallet, and then deciding how the funds from the wallet will be dispersed or stored. (I won't tell you how we are handling that, as that's internal company business, but I'm sure you'll think of something clever, yourselves. Or just google it.)
I would encourage you to arrange to pay yourselves profits. Not merely because your idea is going to make you all fabulously wealthy and internationally famous (although, that is obviously true), but because _profits are the most pure form of communication that consumers in the market have_ with its producers, and one of the best ways to make decisions and measure increases in efficiency (increasing profits and/or output, while keeping prices steady or falling).
Cutting off this signal, in order to look pious to outsiders, is to shoot yourself in your free-market foot. Nobody says that you have to spend your profits on the proverbial _lambo and a bimbo_. You could donate them to charity, reinvest them, or store them for your nephews to inherit, but **pay them out, you should**. You don't have to love money, to value it as a tool and use it shrewdly. Money is a measure, and companies should regularly measure themselves: against their previous state, against their potential state, and against their competition.
(Also, you can use money to buy a lambo and a bimbo, but you didn't hear that from me.)
## Organize yourselves
Once you've been working together, for a while, you'll find that you need to figure out how to organize yourselves. The first step is to...
### Form a board of directors.
Stop laughing. I'm serious.
Any company has at least two roles (President and Secretary), ideally held by two different people, so any single-proprietor company is a man down. Find a different person, to be your Second, even if they're just your confident, who lets you cry on your shoulder on The Bad Days, when your code refuses to compile, and can tell people that you've become a Bitcoin millionaire and have gone on a sabbatical to hike the Himalayas and will be back in 3 months on The Very Good Days.
Because business man was not meant to be alone.
If, like us, you're a small herd of people and have already been working together for a while, then this step is actually really, really fun. Just think about what people are already doing, and put a label on it. That role is now defined and it is clear who is in charge of what.
Scientists become "Chief Science Officer" or "Scientific Advisor". The person who always writes the _okay, so this is what we've decided_ comment in the thread becomes the Secretary, the one managing the Lightning wallet and worrying over paying for the servers is the CFO, the person running the remote server becomes the CTO, and so on and etc.
And everyone knows who the CEO is. Everyone always knows. They do. Just write it down.
### Agree how to disagree
Now, have the secretary write up a Member's Agreement. It's a contract between the members, about whatever the group thinks is important concerning the way the company will operate. According to [Investopedia](https://www.investopedia.com/terms/l/llc-operating-agreement.asp), common topics are:
Is this legally binding? Probably not. Maybe. I don't know and wouldn't tell you, even if I did. But it's _emotionally binding_, which is arguably more important.
Writing things down is an advanced form of _naming things_ and it provides clarity, helps to manage expectations, and allows you to define a working agreement before Real Money shows up and taints your interaction. You're just accepting tips, at the moment. Everyone is calm and cheerful, so now is your best time to negotiate.
Keep it very simple and only address the most basic things. If you wish to incorporate, at a later date, then you just take this to a registered agent, or other experienced person, and have them tidy up any loose ends and add the fine print.
## Go forth, together
This has probably taken you weeks, or even months, but you're now a company. Get a logo and a company npub, start dropping the company name into your notes, and get on with the business of being in business.
-

@ b6ca2216:f45f8b5b
2024-10-20 00:19:37
my 3. article
-

@ b6ca2216:f45f8b5b
2024-10-20 00:16:38
{"id":12345,"title":"deleted","body":"deleted"}
-

@ b6ca2216:f45f8b5b
2024-10-19 23:51:01
{id:123, title:"my first article", body:"This NIP defines kind:30402: an addressable event to describe classified listings that list any arbitrary product, service, or other thing for sale or offer and includes enough structured metadata to make them useful.
The category of classifieds includes a very broad range of physical goods, services, work opportunities, rentals, free giveaways, personals, etc. and is distinct from the more strictly structured marketplaces defined in NIP-15 that often sell many units of specific products through very specific channels.
The structure of these events is very similar to NIP-23 long-form content events."}
-

@ a95c6243:d345522c
2024-10-19 08:58:08
Ein Lämmchen löschte an einem Bache seinen Durst. Fern von ihm, aber näher der Quelle, tat ein Wolf das gleiche. Kaum erblickte er das Lämmchen, so schrie er:
"Warum trübst du mir das Wasser, das ich trinken will?"
"Wie wäre das möglich", erwiderte schüchtern das Lämmchen, "ich stehe hier unten und du so weit oben; das Wasser fließt ja von dir zu mir; glaube mir, es kam mir nie in den Sinn, dir etwas Böses zu tun!"
"Ei, sieh doch! Du machst es gerade, wie dein Vater vor sechs Monaten; ich erinnere mich noch sehr wohl, daß auch du dabei warst, aber glücklich entkamst, als ich ihm für sein Schmähen das Fell abzog!"
"Ach, Herr!" flehte das zitternde Lämmchen, "ich bin ja erst vier Wochen alt und kannte meinen Vater gar nicht, so lange ist er schon tot; wie soll ich denn für ihn büßen."
"Du Unverschämter!" so endigt der Wolf mit erheuchelter Wut, indem er die Zähne fletschte. "Tot oder nicht tot, weiß ich doch, daß euer ganzes Geschlecht mich hasset, und dafür muß ich mich rächen."
Ohne weitere Umstände zu machen, zerriß er das Lämmchen und verschlang es.
*Das [Gewissen](https://apollo-news.net/das-gewissen-in-corona-jahren-zum-tod-von-gunnar-kaiser/) regt sich selbst bei dem größten Bösewichte; er sucht doch nach Vorwand, um dasselbe damit bei Begehung seiner Schlechtigkeiten zu beschwichtigen.*
Quelle: https://eden.one/fabeln-aesop-das-lamm-und-der-wolf
-

@ 8947a945:9bfcf626
2024-10-17 08:06:55
[](https://stock.adobe.com/stock-photo/id/1010191703)
**สวัสดีทุกคนบน Nostr ครับ** รวมไปถึง **watchers**และ **ผู้ติดตาม**ของผมจาก Deviantart และ platform งานศิลปะอื่นๆนะครับ
ตั้งแต่ต้นปี 2024 ผมใช้ AI เจนรูปงานตัวละครสาวๆจากอนิเมะ และเปิด exclusive content ให้สำหรับผู้ที่ชื่นชอบผลงานของผมเป็นพิเศษ
ผมโพสผลงานผมทั้งหมดไว้ที่เวบ Deviantart และค่อยๆสร้างฐานผู้ติดตามมาเรื่อยๆอย่างค่อยเป็นค่อยไปมาตลอดครับ ทุกอย่างเติบโตไปเรื่อยๆของมัน ส่วนตัวผมมองว่ามันเป็นพิร์ตธุรกิจออนไลน์ ของผมพอร์ตนึงได้เลย
**เมื่อวันที่ 16 กย.2024** มีผู้ติดตามคนหนึ่งส่งข้อความส่วนตัวมาหาผม บอกว่าชื่นชอบผลงานของผมมาก ต้องการจะขอซื้อผลงาน แต่ขอซื้อเป็น NFT นะ เสนอราคาซื้อขายต่อชิ้นที่สูงมาก หลังจากนั้นผมกับผู้ซื้อคนนี้พูดคุยกันในเมล์ครับ

### นี่คือข้อสรุปสั่นๆจากการต่อรองซื้อขายครับ
(หลังจากนี้ผมขอเรียกผู้ซื้อว่า scammer นะครับ เพราะไพ่มันหงายมาแล้ว ว่าเขาคือมิจฉาชีพ)

- Scammer รายแรก เลือกผลงานที่จะซื้อ เสนอราคาซื้อที่สูงมาก แต่ต้องเป็นเวบไซต์ NFTmarket place ที่เขากำหนดเท่านั้น มันทำงานอยู่บน ERC20 ผมเข้าไปดูเวบไซต์ที่ว่านี้แล้วรู้สึกว่ามันดูแปลกๆครับ คนที่จะลงขายผลงานจะต้องใช้ email ในการสมัครบัญชีซะก่อน ถึงจะผูก wallet อย่างเช่น metamask ได้ เมื่อผูก wallet แล้วไม่สามารถเปลี่ยนได้ด้วย ตอนนั้นผมใช้ wallet ที่ไม่ได้ link กับ HW wallet ไว้ ทดลองสลับ wallet ไปๆมาๆ มันทำไม่ได้ แถมลอง log out แล้ว เลข wallet ก็ยังคาอยู่อันเดิม อันนี้มันดูแปลกๆแล้วหนึ่งอย่าง เวบนี้ค่า ETH ในการ mint **0.15 - 0.2 ETH** … ตีเป็นเงินบาทนี่แพงบรรลัยอยู่นะครับ

- Scammer รายแรกพยายามชักจูงผม หว่านล้อมผมว่า แหม เดี๋ยวเขาก็มารับซื้องานผมน่า mint งานเสร็จ รีบบอกเขานะ เดี๋ยวเขารีบกดซื้อเลย พอขายได้กำไร ผมก็ได้ค่า gas คืนได้ แถมยังได้กำไรอีก ไม่มีอะไรต้องเสีนจริงมั้ย แต่มันเป้นความโชคดีครับ เพราะตอนนั้นผมไม่เหลือทุนสำรองที่จะมาซื้อ ETH ได้ ผมเลยต่อรองกับเขาตามนี้ครับ :
1. ผมเสนอว่า เอางี้มั้ย ผมส่งผลงานของผมแบบ low resolution ให้ก่อน แลกกับให้เขาช่วยโอน ETH ที่เป็นค่า mint งานมาให้หน่อย พอผมได้ ETH แล้ว ผมจะ upscale งานของผม แล้วเมล์ไปให้ ใจแลกใจกันไปเลย ... เขาไม่เอา
2. ผมเสนอให้ไปซื้อที่ร้านค้าออนไลน์ buymeacoffee ของผมมั้ย จ่ายเป็น USD ... เขาไม่เอา
3. ผมเสนอให้ซื้อขายผ่าน PPV lightning invoice ที่ผมมีสิทธิ์เข้าถึง เพราะเป็น creator ของ Creatr ... เขาไม่เอา
4. ผมยอกเขาว่างั้นก็รอนะ รอเงินเดือนออก เขาบอก ok
สัปดาห์ถัดมา มี scammer คนที่สองติดต่อผมเข้ามา ใช้วิธีการใกล้เคียงกัน แต่ใช้คนละเวบ แถมเสนอราคาซื้อที่สูงกว่าคนแรกมาก เวบที่สองนี้เลวร้ายค่าเวบแรกอีกครับ คือต้องใช้เมล์สมัครบัญชี ไม่สามารถผูก metamask ได้ พอสมัครเสร็จจะได้ wallet เปล่าๆมาหนึ่งอัน ผมต้องโอน ETH เข้าไปใน wallet นั้นก่อน เพื่อเอาไปเป็นค่า mint NFT **0.2 ETH**
ผมบอก scammer รายที่สองว่า ต้องรอนะ เพราะตอนนี้กำลังติดต่อซื้อขายอยู่กับผู้ซื้อรายแรกอยู่ ผมกำลังรอเงินเพื่อมาซื้อ ETH เป็นต้นทุนดำเนินงานอยู่ คนคนนี้ขอให้ผมส่งเวบแรกไปให้เขาดูหน่อย หลังจากนั้นไม่นานเขาเตือนผมมาว่าเวบแรกมันคือ scam นะ ไม่สามารถถอนเงินออกมาได้ เขายังส่งรูป cap หน้าจอที่คุยกับผู้เสียหายจากเวบแรกมาให้ดูว่าเจอปัญหาถอนเงินไม่ได้ ไม่พอ เขายังบลัฟ opensea ด้วยว่าลูกค้าขายงานได้ แต่ถอนเงินไม่ได้
**Opensea ถอนเงินไม่ได้ ตรงนี้แหละครับคือตัวกระตุกต่อมเอ๊ะของผมดังมาก** เพราะ opensea อ่ะ ผู้ใช้ connect wallet เข้ากับ marketplace โดยตรง ซื้อขายกันเกิดขึ้น เงินวิ่งเข้าวิ่งออก wallet ของแต่ละคนโดยตรงเลย opensea เก็บแค่ค่า fee ในการใช้ platform ไม่เก็บเงินลูกค้าไว้ แถมปีนี้ค่า gas fee ก็ถูกกว่า bull run cycle 2020 มาก ตอนนี้ค่า gas fee ประมาณ 0.0001 ETH (แต่มันก็แพงกว่า BTC อยู่ดีอ่ะครับ)
ผมเลยเอาเรื่องนี้ไปปรึกษาพี่บิท แต่แอดมินมาคุยกับผมแทน ทางแอดมินแจ้งว่ายังไม่เคยมีเพื่อนๆมาปรึกษาเรื่องนี้ กรณีที่ผมทักมาถามนี่เป็นรายแรกเลย แต่แอดมินให้ความเห็นไปในทางเดียวกับสมมุติฐานของผมว่าน่าจะ scam ในเวลาเดียวกับผมเอาเรื่องนี้ไปถามในเพจ NFT community คนไทนด้วย ได้รับการ confirm ชัดเจนว่า scam และมีคนไม่น้อยโดนหลอก หลังจากที่ผมรู้ที่มาแล้ว ผมเลยเล่นสงครามปั่นประสาท scammer ทั้งสองคนนี้ครับ เพื่อดูว่าหลอกหลวงมิจฉาชีพจริงมั้ย
โดยวันที่ 30 กย. ผมเลยปั่นประสาน scammer ทั้งสองรายนี้ โดยการ mint ผลงานที่เขาเสนอซื้อนั่นแหละ ขึ้น opensea
แล้วส่งข้อความไปบอกว่า
mint ให้แล้วนะ แต่เงินไม่พอจริงๆว่ะโทษที เลย mint ขึ้น opensea แทน พอดีบ้านจน ทำได้แค่นี้ไปถึงแค่ opensea รีบไปซื้อล่ะ มีคนจ้องจะคว้างานผมเยอะอยู่ ผมไม่คิด royalty fee ด้วยนะเฮ้ย เอาไปขายต่อไม่ต้องแบ่งกำไรกับผม
เท่านั้นแหละครับ สงครามจิตวิทยาก็เริ่มขึ้น แต่เขาจนมุม กลืนน้ำลายตัวเอง
ช็อตเด็ดคือ
เขา : เนี่ยอุส่ารอ บอกเพื่อนในทีมว่าวันจันทร์ที่ 30 กย. ได้ของแน่ๆ เพื่อนๆในทีมเห็นงานผมแล้วมันสวยจริง เลยใส่เงินเต็มที่ 9.3ETH (+ capture screen ส่งตัวเลขยอดเงินมาให้ดู)ไว้รอโดยเฉพาะเลยนะ
ผม : เหรอ ... งั้น ขอดู wallet address ที่มี transaction มาให้ดูหน่อยสิ
เขา : 2ETH นี่มัน 5000$ เลยนะ
ผม : แล้วไง ขอดู wallet address ที่มีการเอายอดเงิน 9.3ETH มาให้ดูหน่อย ไหนบอกว่าเตรียมเงินไว้มากแล้วนี่ ขอดูหน่อย ว่าใส่ไว้เมื่อไหร่ ... เอามาแค่ adrress นะเว้ย ไม่ต้องทะลึ่งส่ง seed มาให้
เขา : ส่งรูปเดิม 9.3 ETH มาให้ดู
ผม : รูป screenshot อ่ะ มันไม่มีความหมายหรอกเว้ย ตัดต่อเอาก็ได้ง่ายจะตาย เอา transaction hash มาดู ไหนว่าเตรียมเงินไว้รอ 9.3ETH แล้วอยากซื้องานผมจนตัวสั่นเลยไม่ใช่เหรอ ถ้าจะส่ง wallet address มาให้ดู หรือจะช่วยส่ง 0.15ETH มาให้ยืม mint งานก่อน แล้วมากดซื้อ 2ETH ไป แล้วผมใช้ 0.15ETH คืนให้ก็ได้ จะซื้อหรือไม่ซื้อเนี่ย
เขา : จะเอา address เขาไปทำไม
ผม : ตัดจบ รำคาญ ไม่ขายให้ละ
เขา : 2ETH = 5000 USD เลยนะ
ผม : แล้วไง
ผมเลยเขียนบทความนี้มาเตือนเพื่อนๆพี่ๆทุกคนครับ เผื่อใครกำลังเปิดพอร์ตทำธุรกิจขาย digital art online แล้วจะโชคดี เจอของดีแบบผม
-----------
### ทำไมผมถึงมั่นใจว่ามันคือการหลอกหลวง แล้วคนโกงจะได้อะไร
[](https://stock.adobe.com/stock-photo/id/1010196295)
อันดับแรกไปพิจารณาดู opensea ครับ เป็นเวบ NFTmarketplace ที่ volume การซื้อขายสูงที่สุด เขาไม่เก็บเงินของคนจะซื้อจะขายกันไว้กับตัวเอง เงินวิ่งเข้าวิ่งออก wallet ผู้ซื้อผู้ขายเลย ส่วนทางเวบเก็บค่าธรรมเนียมเท่านั้น แถมค่าธรรมเนียมก็ถูกกว่าเมื่อปี 2020 เยอะ ดังนั้นการที่จะไปลงขายงานบนเวบ NFT อื่นที่ค่า fee สูงกว่ากันเป็นร้อยเท่า ... จะทำไปทำไม
ผมเชื่อว่า scammer โกงเงินเจ้าของผลงานโดยการเล่นกับความโลภและความอ่อนประสบการณ์ของเจ้าของผลงานครับ เมื่อไหร่ก็ตามที่เจ้าของผลงานโอน ETH เข้าไปใน wallet เวบนั้นเมื่อไหร่ หรือเมื่อไหร่ก็ตามที่จ่ายค่า fee ในการ mint งาน เงินเหล่านั้นสิ่งเข้ากระเป๋า scammer ทันที แล้วก็จะมีการเล่นตุกติกต่อแน่นอนครับ เช่นถอนไม่ได้ หรือซื้อไม่ได้ ต้องโอนเงินมาเพิ่มเพื่อปลดล็อค smart contract อะไรก็ว่าไป แล้วคนนิสัยไม่ดีพวกเนี้ย ก็จะเล่นกับความโลภของคน เอาราคาเสนอซื้อที่สูงโคตรๆมาล่อ ... อันนี้ไม่ว่ากัน เพราะบนโลก NFT รูปภาพบางรูปที่ไม่ได้มีความเป็นศิลปะอะไรเลย มันดันขายกันได้ 100 - 150 ETH ศิลปินที่พยายามสร้างตัวก็อาจจะมองว่า ผลงานเรามีคนรับซื้อ 2 - 4 ETH ต่องานมันก็มากพอแล้ว (จริงๆมากเกินจนน่าตกใจด้วยซ้ำครับ)
บนโลกของ BTC ไม่ต้องเชื่อใจกัน โอนเงินไปหากันได้ ปิดสมุดบัญชีได้โดยไม่ต้องเชื่อใจกัน
บบโลกของ ETH **"code is law"** smart contract มีเขียนอยู่แล้ว ไปอ่าน มันไม่ได้ยากมากในการทำความเข้าใจ ดังนั้น การจะมาเชื่อคำสัญญาจากคนด้วยกัน เป็นอะไรที่ไม่มีเหตุผล
ผมไปเล่าเรื่องเหล่านี้ให้กับ community งานศิลปะ ก็มีทั้งเสียงตอบรับที่ดี และไม่ดีปนกันไป มีบางคนยืนยันเสียงแข็งไปในทำนองว่า ไอ้เรื่องแบบเนี้ยไม่ได้กินเขาหรอก เพราะเขาตั้งใจแน่วแน่ว่างานศิลป์ของเขา เขาไม่เอาเข้ามายุ่งในโลก digital currency เด็ดขาด ซึ่งผมก็เคารพมุมมองเขาครับ แต่มันจะดีกว่ามั้ย ถ้าเราเปิดหูเปิดตาให้ทันเทคโนโลยี โดยเฉพาะเรื่อง digital currency , blockchain โดนโกงทีนึงนี่คือหมดตัวกันง่ายกว่าเงิน fiat อีก
อยากจะมาเล่าให้ฟังครับ และอยากให้ช่วยแชร์ไปให้คนรู้จักด้วย จะได้ระวังตัวกัน
## Note
- ภาพประกอบ cyber security ทั้งสองนี่ของผมเองครับ ทำเอง วางขายบน AdobeStock
- อีกบัญชีนึงของผม "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw กำลังค่อยๆเอาผลงานจากโลกข้างนอกเข้ามา nostr ครับ ตั้งใจจะมาสร้างงานศิลปะในนี้ เพื่อนๆที่ชอบงาน จะได้ไม่ต้องออกไปหาที่ไหน
ผลงานของผมครับ
- Anime girl fanarts : [HikariHarmony](https://linktr.ee/hikariharmonypatreon)
- [HikariHarmony on Nostr](https://shorturl.at/I8Nu4)
- General art : [KeshikiRakuen](https://linktr.ee/keshikirakuen)
- KeshikiRakuen อาจจะเป็นบัญชี nostr ที่สามของผม ถ้าไหวครับ
-

@ 8947a945:9bfcf626
2024-10-17 07:33:00
[](https://stock.adobe.com/stock-photo/id/1010191703)
**Hello everyone on Nostr** and all my **watchers**and **followers**from DeviantArt, as well as those from other art platforms
I have been creating and sharing AI-generated anime girl fanart since the beginning of 2024 and have been running member-exclusive content on Patreon.
I also publish showcases of my artworks to Deviantart. I organically build up my audience from time to time. I consider it as one of my online businesses of art. Everything is slowly growing
**On September 16**, I received a DM from someone expressing interest in purchasing my art in NFT format and offering a very high price for each piece. We later continued the conversation via email.

### Here’s a brief overview of what happened

- The first scammer selected the art they wanted to buy and offered a high price for each piece.
They provided a URL to an NFT marketplace site running on the Ethereum (ETH) mainnet or ERC20. The site appeared suspicious, requiring email sign-up and linking a MetaMask wallet. However, I couldn't change the wallet address later.
The minting gas fees were quite expensive, ranging from **0.15 to 0.2 ETH**

- The scammers tried to convince me that the high profits would easily cover the minting gas fees, so I had nothing to lose.
Luckily, I didn’t have spare funds to purchase ETH for the gas fees at the time, so I tried negotiating with them as follows:
1. I offered to send them a lower-quality version of my art via email in exchange for the minting gas fees, but they refused.
2. I offered them the option to pay in USD through Buy Me a Coffee shop here, but they refused.
3. I offered them the option to pay via Bitcoin using the Lightning Network invoice , but they refused.
4. I asked them to wait until I could secure the funds, and they agreed to wait.
The following week, a second scammer approached me with a similar offer, this time at an even higher price and through a different NFT marketplace website.
This second site also required email registration, and after navigating to the dashboard, it asked for a minting fee of **0.2 ETH**. However, the site provided a wallet address for me instead of connecting a MetaMask wallet.
I told the second scammer that I was waiting to make a profit from the first sale, and they asked me to show them the first marketplace. They then warned me that the first site was a scam and even sent screenshots of victims, including one from OpenSea saying that Opensea is not paying.
**This raised a red flag**, and I began suspecting I might be getting scammed. On OpenSea, funds go directly to users' wallets after transactions, and OpenSea charges a much lower platform fee compared to the previous crypto bull run in 2020. Minting fees on OpenSea are also significantly cheaper, around 0.0001 ETH per transaction.
I also consulted with Thai NFT artist communities and the ex-chairman of the Thai Digital Asset Association. According to them, no one had reported similar issues, but they agreed it seemed like a scam.
After confirming my suspicions with my own research and consulting with the Thai crypto community, I decided to test the scammers’ intentions by doing the following
I minted the artwork they were interested in, set the price they offered, and listed it for sale on OpenSea. I then messaged them, letting them know the art was available and ready to purchase, with no royalty fees if they wanted to resell it.
They became upset and angry, insisting I mint the art on their chosen platform, claiming they had already funded their wallet to support me. When I asked for proof of their wallet address and transactions, they couldn't provide any evidence that they had enough funds.
Here’s what I want to warn all artists in the DeviantArt community or other platforms
If you find yourself in a similar situation, be aware that scammers may be targeting you.
-----------
### My Perspective why I Believe This is a Scam and What the Scammers Gain
[](https://stock.adobe.com/stock-photo/id/1010196295)
From my experience with BTC and crypto since 2017, here's why I believe this situation is a scam, and what the scammers aim to achieve
First, looking at OpenSea, the largest NFT marketplace on the ERC20 network, they do not hold users' funds. Instead, funds from transactions go directly to users’ wallets. OpenSea’s platform fees are also much lower now compared to the crypto bull run in 2020. This alone raises suspicion about the legitimacy of other marketplaces requiring significantly higher fees.
I believe the scammers' tactic is to lure artists into paying these exorbitant minting fees, which go directly into the scammers' wallets. They convince the artists by promising to purchase the art at a higher price, making it seem like there's no risk involved. In reality, the artist has already lost by paying the minting fee, and no purchase is ever made.
In the world of Bitcoin (BTC), the principle is "Trust no one" and “Trustless finality of transactions” In other words, transactions are secure and final without needing trust in a third party.
In the world of Ethereum (ETH), the philosophy is "Code is law" where everything is governed by smart contracts deployed on the blockchain. These contracts are transparent, and even basic code can be read and understood. Promises made by people don’t override what the code says.
I also discuss this issue with art communities. Some people have strongly expressed to me that they want nothing to do with crypto as part of their art process. I completely respect that stance.
However, I believe it's wise to keep your eyes open, have some skin in the game, and not fall into scammers’ traps. Understanding the basics of crypto and NFTs can help protect you from these kinds of schemes.
If you found this article helpful, please share it with your fellow artists.
Until next time
Take care
## Note
- Both cyber security images are mine , I created and approved by AdobeStock to put on sale
- I'm working very hard to bring all my digital arts into Nostr to build my Sats business here to my another npub "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw
Link to my full gallery
- Anime girl fanarts : [HikariHarmony](https://linktr.ee/hikariharmonypatreon)
- [HikariHarmony on Nostr](https://shorturl.at/I8Nu4)
- General art : [KeshikiRakuen](https://linktr.ee/keshikirakuen)
-

@ 472f440f:5669301e
2024-10-16 01:57:41
Over the last four years bitcoin has, among other things, established itself as an incredible corporate treasury asset that benefits those who adopt it as such. Microstrategy is the shining example of this theme going from a company that was hovering barely above a ~$1B market cap in mid-2020 to a ~$40B market cap company holding more than 1% of the 21,000,000 bitcoin that will ever exist. Microstrategy's success has emboldened a number of other publicly trader companies to follow suit. Bitcoin as a corporate treasury asset is well on its way to becoming a standard. If you run a business that doesn't hold bitcoin on its balance sheet you are doing yourself, your customers and your shareholders a disservice.
This is a trend that has its legs under it and will accelerate moving forward. A trend that I believe will emerge this cycle is incorporating bitcoin into real estate markets. Leon Wankum has been beating the drum about this for the last few years and I had the pleasure of sitting down with him this morning to record an episode of TFTC that will be published tomorrow morning. Leon is a real estate developer in Germany and he has made it his mission to educate and warn others in real estate about the demonetization of real estate that is under way due to the fact that bitcoin exists and it provides a far superior alternative.
These are pretty stark numbers. Nothing highlights the superior monetary properties of bitcoin better than looking at a chart of the average price of a home priced in USD v. bitcoin.
Since 2016: +46% in USD -99% in BTC
Since 2020: +34% in USD -70% in BTC
The funny thing is that an overwhelming majority of the individuals who make their living in real estate markets do not understand that this is happening to them. Many think they are doing exceptionally well all things considered. Sure, there may be a bit of a slow down and price retraction due to a couple of years of relatively elevated interest rates, but don't worry! The Fed is lowering rates again and the good times are about to start back up. Nothing could be further from the truth. This trend is going to continue unabated until bitcoin is fully monetized and those is the real estate industry, particularly real estate developers and those who lend capital to developers, should seriously take the time to understand what is happening to them.
Real estate is the largest store of value asset in the world at the moment. The most common number that is thrown around for the total size of the market is $300 TRILLION. $300 TRILLION of wealth being stored in an asset that is illiquid, comes with maintenance costs, taxes, insurance premiums, and susceptible to extreme weather event, among other things. Compared to bitcoin - which is extremely liquid, saleable, divisible and hard to confiscate, real estate is a far superior asset to store your wealth in. This is something that I'm sure is well understood by many of you reading this letter.
What's less understood is the dynamics of the real estate development market over the last few years, which have been severely hindered by elevated interest rates. The higher interest rate environment coupled with the inflationary pressures that forced rates higher in the first place have put developers in a predicament; they have a higher cost of capital to start new projects with raw material prices that are still much higher than they were before the economic lock downs of 2020-2022. This has led to a scenario where it isn't advantageous to start new projects and the projects that broke ground in 2021-2023 are finding that they need to incur more debt to get their developments across the finish line.
Despite the fact that interest rates are on their way back down, it doesn't seem like the economics of these projects are going to materially improve in the short to medium-term as headline inflation begins to creep back up. Couple this with the fact that the jobs market is cratering while real wages struggle to keep up with inflation and many builders are going to find themselves in a situation where they do actually complete a development problem but their cash flow suffers because their customers can't afford the inflated rents that builders will have to charge to get a return on their outlaid capital. Many will be put in a situation where they are forced to be happy with lower rents (cash flow) or sit on the sidelines making no cash flow.
The post-1971 era that brought with it a booming real estate industry is suffering the same fate as the bond market; the generation bull market is over. Real estate prices may go up, but that will be nothing more than a mirage of wealth creation. The unit of account those prices are built on is in dollars, which are being debased at an accelerating rate. Developers, banks and borrowers need to de-risk their real estate exposure and, as Leon points out, bitcoin is the only way to do this in an effective way.
Moving forward developers will have to finance by dual collateralizing their debt with the real estate and bitcoin. In the graphic below Leon illustrates what this type of financing structure will look like. Instead of taking $10m of debt to finance a project and putting it all into materials, construction and marketing, a developer will take out a $10m loan, put $1m in bitcoin and the rest toward the development project. Over the course of the construction of the real estate project, bitcoin will sit in the credit structure and, if held for 4+ years, should increase significantly in value. Saving the builder from risk of default and providing him some optionality in terms of what he can do with the project once it's finished.
In this scenario downside risk is contained - a developer isn't pouring all of the cash into bitcoin at the beginning so the worst case scenario is that bitcoin goes to zero (highly unlikely) and they can eat the small loss and hope to make up with it via cash flows once a project is finished, while upside potential is enormous. Bitcoin is still monetizing and having exposure to the hardest monetary asset the world has ever while it's monetizing has proven to be massively beneficial.
We are still in the early days of bitcoin and this idea will likely seem absolutely insane to most Tradfi investors, but I strongly believe that developers, banks and end consumers who don't leverage this type of bitcoin structured credit will be cooked in the long-run. And those that take advantage of this type of structure first will be considered geniuses in 20 years.
There are many more nuanced benefits to this strategy; holding bitcoin allows landlords and management companies to weather ongoing maintenance costs throughout the years, those who take out mortgages dual collateralized with a house and bitcoin not only protect the equity value of their property but could see their equity values increase significantly more than others using vanilla mortgages, and builders who accumulate bitcoin in their treasuries will be able to use better raw materials when building, which leads to more valuable properties that cash flow for longer.
Again, it's going to take time for these types of structures to become commonplace in the market, but I firmly believe this cycle will be the cycle that these strategies get off the ground. In four to five years they will have a track record and after that it will be considered irresponsible not to finance real estate in this way. The banks will begin to demand it.
---
Final thought...
Sinus congestion sucks.
-

@ eac63075:b4988b48
2024-10-15 20:18:52
Bitcoin emerged as a promise of financial freedom, challenging the traditional and centralized structures of governments and financial institutions. Since its inception, many enthusiasts have believed in the revolutionary potential of this cryptocurrency. However, over the years, challenges have arisen that have tested this promise, especially concerning centralization, the implementation of secondary layers like the Lightning Network, and issues of governance and privacy.
https://www.fountain.fm/episode/SDZYaFMyLEO1krL6x8RD
## **Centralization and the Exclusivity of Nostr**
Nostr, a decentralized network aiming to be censorship resistant, emerged as an attempt to solve some inherent problems of centralization. However, it faces significant challenges. Many users point out that, despite its promise, Nostr is still not attractive to the general public, being exclusive to a specific niche.
Additionally, issues of centralization still permeate the network. Discussions on GitHub revealed that developers chose not to implement an absolute level of privacy, a decision many considered inadequate. Even with protocols developed to ensure total privacy—such as the non-identification of IPs and communicating parties—the network still lacks this robust implementation.
## **Individual Freedom and Data Protection**
A recurring issue is the importance of demonstrating that real options exist for citizens to protect and preserve their freedom. In a world where most discussions about Bitcoin revolve around its use as an investment asset, there is an urgent need to emphasize its potential as a tool for financial freedom.
The Bitcoin community should focus on development and education, showing that the conscious use of cryptography and decentralized transactions can protect individuals against excessive government surveillance and control. Secure and private communication is fundamental, and Bitcoin, along with privacy technologies, can provide this.
## **Hyperbitcoinization and the Illusion of Store of Value**
Hyperbitcoinization is a concept that refers to the moment when Bitcoin will replace fiat currencies worldwide. However, achieving this state is not simple, especially when Bitcoin is seen primarily as a store of value. Since 2017, this narrative has gained strength, promoting the idea that accumulating Bitcoin will lead to automatic wealth.
However, this perspective is limited. The true value of Bitcoin lies in its use as a transactional currency, not just in its scarcity. The community must work to ensure that Bitcoin is utilized in everyday transactions, strengthening its network and demonstrating its real value.
## **The Role of the Community in Bitcoin's Development**
Bitcoin's strength comes from its community. Developers, users, and enthusiasts, through their actions and support, make Bitcoin a powerful tool. This community is responsible for ensuring that Bitcoin maintains its essence and that its functionalities are accessible to all.
It is crucial that this support network continues promoting the decentralized use of Bitcoin, without intermediaries that can censor or control transactions. Adopting Bitcoin in a centralized manner, through banks or other institutions, contradicts its original proposal and strengthens those who have historically opposed its existence.
## **Sidechains, Second Layers, and the Lightning Network**
Sidechains and second layers, like the Lightning Network, are essential components for Bitcoin's scalability. However, they bring challenges, especially regarding the need to trust intermediaries. For these solutions to be effective, it is fundamental that they allow the unilateral withdrawal of funds, ensuring that users maintain full control over their assets.
The Lightning Network, for example, is a second layer that allows fast and cheap transactions. However, many users face difficulties when dealing with channels that do not close correctly, resulting in locked funds. These problems must be solved for the network to be truly decentralized and functional.
## **The Fight Against Centralization on the Internet**
Centralization is not a problem exclusive to Bitcoin. The internet as a whole faces similar challenges, with data control concentrated in the hands of a few large technology companies. To ensure freedom of expression and online privacy, it is necessary to decentralize these data clusters.
Projects that seek to decentralize the internet are vital for this mission. They not only complement Bitcoin in its quest for financial freedom but also ensure that digital communication and expression are protected against censorship and corporate control.
## **The Future of Bitcoin and the Need for Action**
The future of Bitcoin depends on the community's action. We cannot expect Bitcoin to automatically become a global medium of exchange. A conscious effort is necessary to build an ecosystem where Bitcoin can flow freely, being used in everyday transactions and valued for its utility.
Moreover, with the imminent arrival of central bank digital currencies (CBDCs), time is of the essence. CBDCs represent a significant challenge, as they can further restrict individuals' financial freedom. Therefore, accelerating Bitcoin adoption and ensuring it maintains its decentralized and uncensorable properties is a priority.
## **Conclusion**
Bitcoin remains a powerful tool for financial freedom but faces significant challenges. Centralization, both in the context of secondary networks and the internet in general, poses a threat to its original proposal. However, with the joint action of the community and the continuous development of decentralized solutions, it is possible to maintain Bitcoin as a bastion of individual freedom.
The true revolution of Bitcoin lies in its use as a medium of exchange, not just as a store of value. To achieve hyperbitcoinization, it is necessary to build a robust ecosystem where Bitcoin can circulate freely and be accessible to all. Only then can we fulfill Bitcoin's initial promise and ensure it continues to be a tool for freedom and financial autonomy.
-

@ 599f67f7:21fb3ea9
2024-10-14 19:36:50
Inoiz pentsatu al duzu norbaiti satoshiak modu originalean oparitzea, Bitcoin mundura hurbiltzeko? LNbits zorro batekin NFC opari txartel bat erraz sor dezakezu. Honek LNURLw esteka bat NFC txartelean idatziz funtzionatzen du, eta jasotzaileak bere satoshiak erabili ditzake LNURL gaitutako zorro batekin.
### Zer behar dut?
- LNbits zorroa
- Android telefono bat
- NTAG2* gaitasunak dituen NFC txartela, adibidez NTAG216.
💡 NTAG2* txartelek esteka **bat** idazteko aukera ematen dute. Adibidez, enpresaren webgunerako URLa duen bisita-txartel gisa joka dezakete. NTAG424 txartelek ez dute memoria handiagoa bakarrik, baizik eta SUN parametro deitzen den zerbait ere badute, zerbitzariaren autentifikazioa ahalbidetzen duena, eta horrek segurtasun gehiago ematen die zure ordainketei. Azkenean txartel mota hau [BoltCard](https://boltcard.org/) bat bihur daiteke.
### 1. Hedapena aktibatu
Ireki zure LNbits zorroa. Tresna-barran, aktibatu `Withdraw Links` hedapena eta ondoren joan hedapenera.
### 2. Erretiratzeko esteka sortu
`Withdraw Links` hedapen orrian, aukeratu `Advanced Withdraw Link(s)` aukera.
Ondoren, aukeratu satoshiak ateratzeko erabiliko duzun zorroa. Ziurrenik, hori zure LNbits zorro nagusitik bereizi nahi izango duzu. Horretarako, LNbits zorro berri bat sor dezakezu tresna-barratik, `+ Add a new wallet` aukera hautatuz. Behin zorro berria sortuta, sartu satoshi batzuk bertan.

Eman izenburu bat erretiratzeko estekari.
Ezarri erreskatatu daitezkeen gutxieneko eta gehienezko zenbatekoak.
Ezarri esteka zenbat aldiz erabil daitekeen eta erretiratze saiakeren arteko denbora.
Aukeran, argazki pertsonalizatu bat gehi dezakezu `Use a custom voucher design` laukitxoa markatuz, eta .png irudi baten URL-a sartuz.
Gogoan izan “assmilking” laukitxoa ez markatzea.
Konfigurazioa amaitu ondoren, jarraitu erretiratzeko esteka sortzera.
### 3. Idatzi esteka NFC txartelean
Zure erretiratzeko esteka berrian, klikatu `View LNURL` estekan. Ondoren, sakatu `Write to NFC` botoia eta eutsi NFC txartela telefonoaren aurrean idazketa-prozesua burutzeko.

✔️ **EGINDA**
💡 Esan txartelaren jasotzaileari satoshi saldoari buruz, denbora ez dezan galdu azkeneko satoshia lortzen saiatzeko.
💡 Jasotzaileak txartelaren satoshiak atera ondoren, bere zorroan berridatzi dezake eta berrerabili. Gainera, eman diozun txartela NTAG424 bada, aurreko gidako (nostr:naddr1qqxnzd3e8qcr2wfn8qcrgwf4qyg8wumn8ghj7mn0wd68ytnhd9hx2q3qtx0k0a7lw62vvqax6p3ku90tccgdka7ul4radews2wrdsg0m865sxpqqqp65whwqrr5) bezala Lightning "zor txartela" bihur dezake. Baina txartela NTAG2* bakarrik bada, beste opari txartel bat bihur dezake soilik.
-

@ 5e5fc143:393d5a2c
2024-10-11 22:15:54
We are now given a choice of digital freedom #nostr .
Creativity for every nostrich is now unleashed from the cage of bigtech censorship , rules and algo. But freedom comes with responsibility so pick right one(s). I will try share here some learning experience both technical and also from fundamental point of view. Just wanted kick start this article n fill as we go like living reference document.
Nostr itself is an application layer protocol that can used beyond just social media mirco or long blogging. Each nostr client heavily dependent on back-end servers call nostr "Relay servers" or in short "rs" or "relays" Relays can hosted anywhere in clearnet internet, onion net , vpn , i2p , nym
Relays are controlled by their respective admins based NIP specs that they select to implement according to own decisions. Relays can have certain ToS (Terms of Service) Rules to adhered too.
New users can choose and pick client or app (ios / android/ windows) with preset of relays in the simplest form , but other advanced users need to do a regular manual relay management.
Relay management is an active regular task based on where when n how you are using.
Relay list are saved within you npub profile backup file which can edited and broadcast anytime.
Relay management is an active regular task based on where when and how you are using.
Relay list always need to be updated time to time as and when needed.
2 Users MUST a common RELAY between them even if one only need to follow another.
Occasionally you may notice certain npub accounts you are following already but cannot see frequent notes publish by them – one of cause maybe you not sharing a common relay
Most nostr client applications has SETTINGS where user choose add/remove relays
Also user choose which function to enable - READ or WRITE
Relay list for your account is always saved within you npub profile backup file which can edited and broadcast anytime. Hence any app or browser when u login with you npub the same relay list will be enforced. There could valid reasons why u need have list for if you trying to save bandwidth and traveling.
Functions in app.getcurrent.io and primal.net app for mobile apple or android are ideal for user traveling abroad and wanted to save bandwidth since relay management is done the providers in backend and saves hassle for basic usage.
Remember if someone is selecting relay on your behalf then you may not be necessarily able to pull and get some specific and special content that you may need. Such providers like coracle and nostrid also give option to override the default relays they selected.
Relay types: They can be categorized by various features or policy or technologies.
FREE PUBLIC Relays vs PAID PUBLIC Relays
PAID relays provide unrestricted access / write / filtering options than FREE relays but both are public clearnet relays. Just subscribing to PAID relays will not solve all problems unless you choose the relays properly and enable settings correctly.
Private Replay or Tor Relays – normally not easily visible until unless someone tell you.
You can also host own private relay not opened to internet of archive and back of your own notes.
The technical landscape in nostr can be fast changing as more NIPs get proposed or updated.
Relays admin can choose implement certain NIPs or not based on policy or technical limitations.
Example NIP33 defines “long notes” aka blogs as you now reading this in habla site which #1 UI and site for "Editable" long notes – some relays donot implement or allow this.
NIP07 is used for client authentication like nos2x and is implemented by all relays in fact.
Nostr is so fasting changing-hence many links many broken Pushing long note again.
To be continued again ... reference pics will added later also
Hope this help you understand "why when what" to tune and maintain active set of proper relays.
Relay Proxy, Relay aggregator or Relay multiplexer – Paid, Public, Free, Private, Event, Relays
That’s all for now n more later ... Thank you 🙏 ! ⚡️ https://getalby.com/p/captjack ⚡️ PV 💜 🤙
References:
https://habla.news/relays
https://relay.exchange/
https://relays.vercel.app/
https://nostr.info/relays/
https://nostrudel.ninja/#/relays
Related Articles:
https://thebitcoinmanual.com/articles/types-nostr-relays/
nostr:naddr1qqd5c6t8dp6xu6twvukkvctnwss92jfqvehhygzwdaehguszyrtp7w79k045gq80mtnpdxjuzl9t7vjxk52rv80f888y5xsd5mh55qcyqqq823cf39s98
https://habla.news/u/current@getcurrent.io/1694434022411
-

@ 472f440f:5669301e
2024-10-11 14:20:54
As we sprint toward the 2024 US Presidential election the case for using bitcoin as an asset to store value for the long term has never been stronger. The insanity of the incumbent power structure is being laid bare and it is becoming impossible to ignore the headwinds that the Borg faces moving forward.
Yesterday morning and earlier today it became clear that inflation is rearing its head again. Not ideal for the soft landing Jerome Powell and Yellen are signaling to the markets after the first Fed Funds rate cut in years.
It seems like the yield curve predicted this earlier this week when it inverted after a temporary normalizing period after the Fed's rate cut. Futhermore, it is becoming glaringly obvious that running historically high fiscal deficits while interest rates were at multi-decade highs was a pretty bad idea. As James Lavish points out, the data from the CBO earlier this week shows that the US federal government is running a deficit that is 13% higher than it was last year. This is at a time when real wages are still depressed, inflation is still suffocating American consumers and the private sector job market for American citizens is cratering.
Speaking of the job market, the numbers that came in yesterday were worse than expected:
The effect of Hurricane Helene should certainly be taken into consideration when looking at this jobs miss. However, even with the miss we know that these numbers have been under reported for years to make the economy seem healthier than it actually is. Even with Helene's effect taken into consideration this print will likely be revised higher 3-6 months from now.
All of this points to a breaking point. A breaking point for the economy and, more importantly, a breaking point for overall confidence in the US government and its ability to operate with any semblance of fiscal responsibility. The chart that Pierre Rochard shares in the tweet at the top of this letter is the only chart that matters for anyone attempting to gauge where we find ourselves on the path to bitcoin realizing its full potential.
There is $133 TRILLION worth of value sitting in global bond markets. Bitcoin is a far superior asset to store one's wealth in. Bond markets are beholden to the whims of the actors who issue those bonds. In the case of the US Treasury market, the largest bond market in the world, the US government. And as we have pointed out above, the US government is recklessly irresponsible when it comes to issuing debt with a complete inability to pay it back on the long-term. Inflation is up, the jobs market is cratering for the native born Americans who actually pay taxes, and the push toward a multi-polar geopolitical landscape is becoming more pronounced by the day. All of this points to a long-term weakening in demand for US treasuries.
The only way out of this mess is to overtly default on this debt or inflate it away. The latter will most certainly be the route that is taken, which positions bitcoin extremely well as people seek the confines of an asset that cannot be debased because it cannot be controlled by a central authority.
The levels of sovereign debt in the world are staggering. Do not let the bitcoin price consolidation of the last six months lull you into a state of complacency. Even the results of the Presidential election won't have a material effect on these dynamics. Though, a Donald Trump presidency would certainly be preferable if you prefer to see relatively sane policy enacted that would provide you with time to find safety in bitcoin. But, in regards to this sovereign debt crisis, that is the only benefit you can hope for; more time to prepare.
I'll leave you with some thoughts from Porter Stansberry:
"We are about to see the final destruction of the American experiment. Every economist knows this (see below) is correct; but nobody is going to tell you about it. I’ll summarize in plan English: We are fucked.
1. Debt is growing much faster than GD and interest expense is growing much faster than debt; and the real growth in entitlement spending hasn’t even begun yet.
2. Progressive taxation means nobody will ever vote for less spending + the combined size of government employees and dependents, there’s no way for America’s actual taxpayers (about 20m people) to ever win an election, so the spending won’t stop growing and, ironically, inflation will make demands for more spending to grow.
3. Inflation undermines both economic growth and social cohesion. The purple hair man-women weirdos are only the beginning; what comes next is scapegoating jews, blacks, immigrants and a huge increase in violence/domestic terror.
Get ready America. This election has nothing to do with what’s coming. And neither Trump nor Kamala can stop it.
Our experiment in freedom and self-government died in 1971 (when all restraint on government spending was abandoned with the gold standard.) You can only live at the expense of your neighbor until he runs out of money.
And that day is here."
---
Final thought...
I hope my tux still fits for this wedding.
Enjoy your weekend, freaks.Use the code "TFTC" for 15% off
-

@ e88a691e:27850411
2024-10-11 13:17:16
# An opinionated guide to Sauna.
By NVK [🌐](https://primal.net/nvk) [🐦](https://twitter.com/nvk)
## Introduction
Updated from the Sauna, October 7th 2024
After years of experimenting with different sauna types, I’ve developed strong opinions on the subject. The purpose of this article is to share these opinions with anyone who is interested in them and, hopefully, help others get more out of their sauna experience.
I’m certain my opinions will offend some, including all the people who (in my view) are doing it wrong. I know that saunas are important to many cultures around the world and that my strongly held opinions may offend some of those cultures.
Mind you, although I grew up in South America, I do have a fair amount of slavic blood in me. When I was a child, my grandfather regularly took me with him to the shvitz. One of my fondest memories from this time was the “Scottish Bath”, which involves standing against the sauna wall, execution-style, so that someone can spray you with freezing water from a high pressure hose. I’ve never heard of this outside of South American and can’t attest to whether it has any real Scottish origins.
The various health claims about using a sauna are beyond the scope of this article. All I have to say is that, like many things in my life, like Bitcoin, the meat/keto diet, and fasting, I find sauna to be yet another cheat code to life: it’s a simple thing that just makes life a lot better. If you want a good primer on scientific health benefits of sauna, I recommend starting with [this article by Rhonda Patric](https://www.foundmyfitness.com/topics/sauna). She goes in depth.
To be clear, it should go without saying that I am not a medical expert or professional. None of the opinions below are, or should be interpreted as, medical advice. There are many people for whom sauna use is not recommended. It would be prudent for any sauna user to consult with his or her doctor before entering a sauna.
_Thanks to S. for taking the time to do a very helpful first review of this article. And thanks to The Wife for helping make my words legible and helping me make time to sauna–I don’t know which sacrifice was bigger._
## Banya or Nothing
When I talk about saunas, I’m talking about a sauna with a stove, either wood or electric, that allows for steam. I call this “Banya style”. To be clear, I’m distinguishing between saunas and steam baths. Steam baths have their own place, but they aren’t my thing and I don’t consider them saunas.
A breakdown of the main types of saunas may be helpful, so you know which to avoid:
1. Wet saunas, which are typically cedar rooms with wood burning or electric stoves onto which you throw liquid to create steam (I call this “Banya style”);
2. Dry saunas, which are typically cedar rooms with wood burning or electric stoves without added steam (like Korean style saunas); and
3. Infrared saunas, which, unlike traditional saunas, don’t heat the surrounding air. Instead, they use infrared panels to warm your body directly.
In my opinion, it’s Banya style or nothing. I’m not a huge fan of dry saunas, and I don’t even bother with infrared saunas. Infrared is a fiat-shitcoin. I want steam!
## How to Sauna
### Sauna Etiquette
If you read no other part of this already-too-long-article, read this.
Saunas are social places. There are proper ways of being in a sauna with others, and there are ways to do it wrong. You don’t want to be the person who ruins it for everyone. Here are some important etiquette tips:
**Silence vs. Chatting:** It’s not a question of whether you have to stay silent in a sauna or if it’s ok to talk. It depends on the circumstances and who else is around. If you’re using a sauna that isn’t your own, ask the staff about the preferred custom. The noise level in a sauna differs depending on the group in the sauna at a particular time. If you do want to chat with others, there’s nothing wrong with that. But, pay attention to whether there are others in the sauna who'd prefer it quiet. And definitely do NOT be obnoxiously loud – yes, I’m looking at you bachelor(ette) group who just discovered the Russian Banya.
**Coming and Going:** People rotate in and out of the sauna at different paces, so there will be people coming and going during your shvitz. But there are ways to come and go that are considerate and proper.
Keep the f-ing door closed (which was the working title of this article). Once you leave, don’t come back inside moments later. Doing so disturbs your fellow sauna users, lets out the all-important steam, and prevents the sauna from reaching an appropriate temperature.
If you’re in the sauna with a group of friends, try to coordinate your comings and goings so you’re all on the same cycle.
If you can only last 5 min at a sauna, don’t go in too often at the risk of ruining it for others (assuming it’s not your own private sauna).
Be fast when closing the sauna door when you come or leave. Otherwise, you will get dirty looks from others and may even hear mumbles of “quick quick, fast fast” from a Gray Beard. And you will deserve it.
Never open the door right after someone puts water on the stove to make steam. It’s all about the steam. Don’t waste it.
**Controlling the heat:** if you can’t handle the heat in the sauna, don’t just turn the heat down, because it ruins it for others. Instead, go to a lower bench or get out and take your break. Saunas are meant to be hot. That’s the whole point.
**Personal Hygiene:** Shower before you go into the sauna. Don’t wear perfume, smelly deodorant, or fragrant lotions. Smells get amplified in a sauna. Have a towel under you, don't leave your drippings behind. Best yet, make a Z with your towel, this covers your butt and down under your feet.
**Clothing:** sauna is not a place for wearing clothing. It is a place to get back to nature. If you are shy, just wrap a towel around yourself. People ask if I don't feel awkward, the answer is no. Who cares, humans naked is not novel. In many countries, it is strictly forbidden to wear clothing or bring anything but a towel into the sauna. It's understandable that may not be possible in North American public saunas on mix gender "family" days. If you have to wear something, then wear something 100% cotton or marino wool. You don't want plastic being backed into your genitals. One more thing, leave the watch out as it gets hot and will burn you. Also, flip-flops/sandals, stay outside.
Some saunas sell body scrubs and masks for you to apply before or in the sauna. Note that once in the heat, these can get goopy and drippy and may melt into your eyes and mouth. So (in this opinionated guides’ wife’s opinion), they are better in theory than reality.
**Adding Oils and scents:** As discussed below, it can be nice to add certain oils and other scents to the steam. But if there are others in the sauna, ask first before you do.
**Where and how to sit:** Hot air rises. So, the higher benches are hotter and the lower benches are cooler. If you are a newbie, pick a lower bench so you don’t have to leave as quickly and open the door unnecessarily.
It’s great to lay down in the sauna, but if it gets crowded, sit up to make room for others.
When moving around to find your seat, don’t walk on the benches in your sandals. Leave your sandals outside the sauna or on the sauna floor.
### Sauna Temperature
In most proper Russian style Banyas you will find temperatures of 80-95 degrees celsius, which, in my opinion, is the best range. Thats near your body. "Offical" on the dial will he 100-120C. But sometimes you want to take it a little easier or last a little longer in the sauna. In these cases, 65-85 at body, dial at 80-100. degrees celsius will do.
However, if your sauna is below 85 degrees celsius on the dial, you might as well just go hide under your bed sheets and not waste your time.
At some saunas in hotels, gyms, or spas, you may not be allowed to set the sauna as high as you’d like (see below). There are many tricks to circumvent these frustrating restrictions, but my legal counsel has advised me not to go into any details here.
### Sauna Duration
The amount of time you spend in the sauna is a matter of personal preference and depends on the number of cycles you do (more on cycles, below).
For your first round, my opinion is that most people should try to last 15 minutes in the sauna. If a sauna is at the proper temperature, most people will struggle to stay inside any longer. If you can stay inside for 20-30 minutes, your sauna is probably too cold and/or there is not enough steam. Many saunas have hourglasses inside to keep time, and I’ve never seen a sauna hourglass with more than 15 minutes, which should be a good hint.
My preferred is;
Cold Plunge => Sauna 15 min => Cold Plunge => Hydrate with Salt & Water, Rest 5-10min => Sauna 15min => Cold Plunge => Hydrate with Salt & Water, Rest 5-10min => Sauna 15min => Cold Plunge => Hydrate with Salt & Water, Rest
if you can rest in the sun even better (no sunscreen poison please). You can add alcohol drinks to the hydration if you feel comfortable with that. But only add food after the last cycle.
For subsequent rounds, hydration starts to play a bigger role in how long you stay inside. Most people seem to last longer on their first round than on their second or third. If you can do 15 minutes on your second round, great. But 5-10 minutes is also fine.
### Sauna Cycles
The traditional Russian Banya method (and in this writer’s opinion, the best method) is to do sauna cycles. Go into the sauna and just stay as long as you can take it (up to 15 minutes or so). Then take a cold shower and/or cold plunge (see below). Then robe-up and go relax with water, tea or beer. Once you start feeling “normal” again, repeat. For me, three cycles is the sweet spot. I’ll do more cycles if I’m spending the day at the Banya facility. If I’m at home, where I often sauna every other day, I find just one or two cycles does the trick. Sometimes I add a cycle or two on the weekend.
Occasionally, I like to go into the sauna as it’s warming up and before it reaches optimum heat (i.e. at around 60 degree celsius). This way, I can stay longer in the sauna for my first round (about 30-40 minutes). If I take this approach, I generally only do one more short round after my cold plunge.
### Cold showers and plunges
In my experience, you want to take a cold shower or a cold plunge (or both, plunge is better) after the sauna cycle.After you come out of the sauna, immediately jump into cold plunge for a bit, i don't like to stay too long. Some Banya facilities will have a bucket filled with cold water that you can pull with a string to let the water pour over you, pull a couple times. The banyas may also have a cold pool of water into which you can plunge for a bit.

If I’m at my country place, after I get out of the sauna I jump into the cold lake. If it’s winter, I like to roll in the snow, which is satisfying. Some cultures would say that it’s not a real sauna experience unless you roll in at least one foot of snow.
After your cold shower or plunge, put on a warm robe and go relax before going back into the sauna. I like to relax for 5-20 minutes, depending on how much time I have. This allows the body’s temperature to decrease slowly. I do not recommend going directly back into the sauna after your cold plunge. If you don’t give yourself enough time after the cold plunge, you will overheat and won’t last very long when you return to the sauna.
### Position
There really are no rules here. The way you position yourself in the sauna depends on your mood and preference, and there are many options. For example, you can sauna seated with your legs hanging down or with your knees up. You can lie down if there’s room. My favorite position is to lie down on my back with my legs up against the wall and, assuming the ceiling is low enough, with my feet stretched against the ceiling. This is a great way to stretch the hamstrings (check out stretching under “Sauna Activities”, below).
Choosing whether to sit on a higher bencher or lower bench is the best way to control the temperature you experience without adjusting the room temperature itself. You will notice the heat in the sauna increases exponentially every inch you go up. If you are struggling to stay in the sauna but don’t want to get out just yet, try moving down to a lower bench to last a little longer. Lying on the floor is the coolest spot and a great place for kids to start getting exposed to saunas.
- - -
#### There is no shame in going to lower benches or even the floor, there is only shame in opening the door before 15min
- - -
### Getting Steamy
Without steam, the sauna would just be a sad, hot oven (I’m looking at you, infrared sauna).
The steam in the sauna has many benefits but most importantly it increases the thermal coupling of your body to the air and it feels great.
The amount of steam in the sauna is a matter of personal taste. You don’t want to make it into a steam room (remember, steam rooms are NOT saunas). But, you do want the sauna to be very moist. I find that two to four ladles of water in a mid-size sauna every five to seven minutes does the trick. Keep it between 50-60% humidity.
I keep a bucket of water in the sauna at all times so that I can continue to ladle water as I shvitz. Make sure to get a wood bucket and a metal ladle with a wooden handle. Wood ladles will crack, and if the handle is metal, it’ll burn you when you grab it.
If, when you enter the sauna, it’s already been on for a while, the wood is likely to already be wet and the sauna full of steam, so you may not need to add too much water. However, if you’ve just turned on the sauna and the wood walls are dry, you will need to ladle more water to make the air moist enough. If the sauna is too moist for comfort, open the door and let it dry out a bit (obviously, only do this in a private sauna).
Essential oils and even beer can all be added to the water to create scented steam. I recommend starting your sauna with just water, and add the scent as you get going.
You can try all sorts of different essential oils. I’ve tried everything from oak and cedar to tangerine and cinnamon (gag) essential oil. In the end, there are really only two oils that are worth it, in my opinion. The first is eucalyptus. I’ve experimented with different types of eucalyptus oil, and the variety you use makes a difference. My favorite is eucalyptus globulus. I also like diluted pine tar oil.
When you settle on your essential oil, add a healthy dose of the oil to the ladle filled with water. Never put the oil onto the oven directly. It’ll just burn.
In a few Russian facilities, I’ve seen Gray Beards pour Russian beer onto the oven and it was actually quite nice. It’s almost like being in a cozy bakery while you sweat
Some people like to place a salt brick or compressed solid blocks in their sauna from time to time. Put the salt block on the stove and pour water over it. The steam takes on a saltiness that feels nice. If a salt block is not available, you can get a cast iron teapot, fill it up with salt water, and place it on top of the stove.
And for my most important steam tip, I recommend using the “towel spin”. This is an effective and underrated technique to help circulate steam in the sauna. After creating steam, take your towel above your head and spin it around hard, like a ceiling fan. This movement works like a convection oven and spreads and equalizes the heat and steam throughout the room. It might make the folks sitting lower down in the sauna a little hotter, but that's what they’re there for, isn’t it?
### Hydration
Being hydrated is important to having a positive sauna experience. You will lose a lot of your body’s water in the sauna. Ideally, start to hydrate well up to an hour before your sauna. I like to add a pinch of salt to my water to encourage water retention.
Do not bring any drinks into the sauna (the exception being a dedicated steam-beer, see above). Have your water or beverage when you’re outside the sauna, resting. If you find you need to drink water inside the sauna in order to cool yourself down, then it’s time for you to get out and allow your body a cool-down.
When you’re outside the sauna, don’t immediately down a glass of super cold water because you will cool down your internal body too fast. Personally, I like to drink warm tea after my first two cycles. After my second cycle, I enjoy a beer (pre-keto days), soup, or vodka drink. When non-keto, I do enjoy adult drinks in the cycles.
If you are doing a sauna while on a multi-day fast, you need to have water and salt, at a minimum. Otherwise, you will deplete your natural reserve of electrolytes and not be able to think straight.
### Sauna Frequency
When it comes to frequency, if you are not in the equatorial heat do it every day. I now do mornings and end of day if I can. so 2x 2-3x cycles. In the summer, living in a hot & humid location, I sauna a lot less frequently. My desire to sauna is greatly diminished because I spend a lot of time in the sun and heat.
### What to wear
**Sauna Hat:** I highly recommend wearing a Russian/Finish style wool hat when you’re inside the sauna. It may seem counterintuitive, but wearing a hat keeps your head cooler. An overheated head is not good for your brain. Wearing the hat stops you from overheating and lets you stay longer in the sauna. The temperature in a sauna is significantly hotter the higher in the room you are, and one’s head is at the top of the body (for most people). So protect your brain in style with a felt sauna hat. If you don’t have a felt sauna hat, buy one. They are easily found online. But in the meantime, you can wrap a dry towel around your head. Don’t forget to take your sauna hat off as you relax between cycles so your head can cool down.

**Clothing:** These days, many public saunas will have family days, men-only days, and women-only days. For obvious reasons, you’re only allowed to sauna naked if you’re attending one of the single-sex days.
If you’re at home, there’s no good reason to wear shorts or a bathing suit. Sauna naked. It's a lot more pleasant.
If you do wear clothing in the sauna, be careful with items with materials like metal or plastic attached. Things like pins, buttons, or string-ends will get very hot and probably burn you. Remember to take off any heat-conductive jewelry and leave your smart watch outside, as the heat will ruin its battery.
Don’t wear your robe inside the sauna. A robe is what you wear outside when relaxing or eating. If you wear it inside, you’ll overheat (and look like an idiot). Go ahead and sweat out that body shame robe-free. You can bring a towel into the sauna to sit on, if you want.
Shoes or sandals are highly recommended in public facilities. I mean, there are many people walking around wet. Ew. But keep your sandals outside the sauna itself, or on the sauna floor.
### Sauna activities.
Don’t overthink it. Sitting in a sauna is activity enough, in my opinion. But there are some sauna activities you can do:
**Veniks/Viht beating:** these are bundles of leaves (commonly birch, oak, or eucalyptus) that are pre-soaked in hot water. Someone with both strength and capacity to exert themselves in the heat will beat your whole body with the leaves. This exfoliates your skin and also gets the plant oils to permeate your skin. And it’s very relaxing. If you’re at a sauna facility, don’t just grab any bundle you see lying around - that belongs to someone else and veniks aren’t shared. You have to bring your own or buy them at the front desk.
**Stretching:** this is a great activity to do in the sauna, but make sure to go very easy. Your muscles will be super warm and you don’t want to overdo it and hurt yourself.
**Exercise or Sex:** your heart better be in good shape if you try out these high intensity activities in the sauna. If you engage in the latter, you better be in your own home sauna. With respect to the former, I think doing some leg-ups can be very satisfying.
**Phone use:** If you’re at home, it’s nice to use your sauna time to shit-post on Twitter or read an article, if you feel like it. Just keep your phone close to the colder, lower parts near the floor or it’ll overheat and shut down. You can also place the phone outside of the air vent and play a [podcast! The Bitcoin.review is great ;)](https://bitcoin.review)
**Napping:** I don’t recommend this. If you fall asleep or pass out, you will probably die due to overheating or dehydration.
**Chatting:** Saunas are great places for conversations (subject to the caveats I address above). Note that nowadays, microphone modules are both very tiny and can withstand high temperatures, so it’s no longer recommended to reenact mafia movie sauna scenes.
**Eating and Drinking:** As discussed above, never have food or drink inside the sauna. But when you finish your sauna, take advantage of whatever snacks the facility offers. For Russian joints, the soups, fish roe and dry salty fish snacks are great. Again, don’t eat before your sauna; wait until you’re done. Some places will have bottled salty-ish lake water, and beer seems to be a good source of salts and re-hydration. Vodka drinks are nice sometimes, too. My favorites are vodka with beet juice and horseradish, vodka with pickle juice, or just a chilled shot of Zubrowka (vodka infused with bison grass). Teas are also very enjoyable post-sauna. I prefer non-caffeinated berry teas. Some Banyas even offer free tea to patrons.

## Ready to Sweat It Out?
Thanks to this fantastic guide to sauna, you’re now feeling confident and excited to seek out a solid sauna. So where do you go?
## Where to Find a Sauna
**Spas:** Spas are not the best place to have an optimal sauna experience. Saunas at spas are typically not hot enough and spas have annoying staff whose job it is to enforce idiotic rules and practices that prevent you from having a real sauna experience.
**Gyms & Hotels:** These are some of the worst places to sauna. For liability reasons, these saunas tend to be too cold and there are often mechanisms that prevent you from raising the temperature. Here, you’ll often see saunas with glass doors, which may look chic, but are inefficient and stupid because they don’t seal properly and leak steam. Gyms and hotels are high traffic areas, so people who don’t know what they are doing are constantly coming and going from the sauna, which, as we discussed, is a sauna no-no. If you still want to try the sauna at your gym or hotel, I recommend going in naked. It’ll deter people from joining you and ruining the little steam you managed to get going.
**Traditional bath houses (Banyas):** These usually offer a great experience because they deliver a super hot sauna, good cold baths and plunges, delicious food and drinks, and knowledgeable staff.
**Home:** Yes, you can build a great sauna in your own home! You can create a small space in your basement, turn a closet or cold room into a sauna, or just add an outdoor hut or barrel sauna in your backyard. This is the best way for you to control the whole experience and do it often. As with anything, the easier it is to access, the more you will do it.
_Build it. They will Come_
Many people have asked me for details about sauna building. If you’re ready to build your own personal home sauna, here are some important considerations.
#### Materials
Saunas are insulated rooms, most commonly finished with cedar tung and groove slats. Cedar is used because it doesn’t rot with moisture. You don’t want treated wood as it will release all the bad stuff that keeps the wood from rotting into the air when heated. Cedar interior is often placed over a vapor barrier, followed by insulation and then the outer wall. Many outdoor saunas are not insulated. They simply have a single layer of cedar 2x6 planks functioning as both the interior and exterior. Non-insulated saunas need much more heating power in the winter.
#### Structure
For indoor saunas, you may want to find a bricklayer to build something for you. Traditional facilities often have brick-lined rooms and very large wood-burning stoves.
You can buy prefab outdoor saunas, which are often sheds or barrels. After experimenting with both, I’ve concluded that barrel saunas are inferior, even though that’s what I have at my country property. This is because barrels have concave ceilings and inner walls. This means the benches are lower and the curve makes the topmost part of the ceiling (and the hottest part) the furthest from you, or inaccessible. The spinning towel trick really helps in the barrel.
When it comes to buying a sauna, go with the most traditional structure possible. They are based on thousands of years of evolution and knowledge.
Portable tent saunas are fun, but impractical because you have to set them up before each use.
Bench height inside the sauna is important. I think the top-most bench should be very near the ceiling. This way, when you’re lying down, you can use the ceiling to stretch the hamstrings. As a rule of thumb, bench length should allow you to lie down completely. It is also nice to have at least one lower bench for visitors or less intense sauna days.

#### Sauna Ovens
There are two main types of sauna ovens: wood burning and electrical (with gas heating being available, but not common). If the location you are building allows for it, go with electrical. It’s practical and easy to get going quickly. This means you will use it more often. Wood burning saunas are romantic and smell great, but it is a lot more work to get a fire going, especially in the winter.
Opt for oven sizes that are recommended or above recommended for the size of the sauna. A larger oven means more thermic inertia, more rocks for steam, and therefore less time to warm up the room. Bigger is better. The Scandinavians make the best quality ovens.
#### Oven controllers
There are two types of temperature control devices: the analog cooking-style or the digital type. I think, due to liability and safety, all ovens have a timer that max out at one hour.
The digital oven controllers are fantastic and I have one in the city in my basement sauna.
However, you have to consider your environment. For me, temperatures in the winter can reach below -30C and in the summer, over 40C. This massive range can take a toll on outdoor equipment and materials. For this reason, I opted for an analog controller for my outdoor sauna in the country, since the weather will likely ruin the electronics of the digital controller.
I would avoid ovens with analog pre-heat timers. They are great in theory, but the implementation is utter garbage. The timer won’t be precise and it’ll just lead to frustration, for example, when you thought you set the oven to start in three hours, but it actually started in two hours and already turned off.
#### Important Sauna Gear
Windows are nice to have, especially if you have a view to enjoy. Opt for at least a cedar door with a little window. Do not go with modern glass door styles. They are crap. They have gaps, no insulation, and let in too much light.
Saunas need thermometers and hygrometers (to measure humidity). The thermometers should be rated for saunas and be visible inside. This is both for safety and bragging rights.
I think having an hourglass inside your sauna is a must. Being able to know for sure how long you’ve been inside is important, since your sense of timing inside the sauna may be off depending on the state of your mind and body on a given day. You shouldn’t wear a watch inside the sauna, since it’ll overheat or break. Having a clock visible from the inside is also a good idea, especially if you sauna often and have a wife and kids who you don’t want to leave you.
Air circulation is an often-overlooked but important part of a sauna design. Saunas should not have stale air. The best sauna design creates natural “real convection” by placing an air intake under the oven wall and another at the top opposite wall. This allows fresh air to enter the sauna while in use. Be sure to add regulators, since you don’t want to cool the sauna or expel all steam. Without regulators you may get too much or too little air in. With too much air, you may cool the sauna down too much and/or lose too much steam.
#### Nice Things to Have
Lights are optional but welcome additions. It can be unpleasant to have no lighting at all, especially in an outdoor sauna on a cold, dark night. Lights should be warm-temperature and low power. I recommend an oven light, since they don’t sweat the heat (get it?) and are often low power.
Put a baking tray under your oven–thank me later.
Wood “pillows” for your head are nice and don’t get sweat-stained and stinky, like a fabric pillow.
Keep some extra felt hats near your sauna so when you or your guests forget their hat, you still have easy access to one.
I like to keep a couple of essential oils on the floor of the sauna, for easy access. If you keep the oils too high in the sauna, they’ll get too hot and spoil.
I place some duck boards over floor tiles in the sauna to prevent cold feet.
I also like to keep a small, natural broom inside the sauna to sweep up any dirt or leaves that come into the sauna on people’s feet.
## Final words
As you can tell, I have some strong opinions when it comes to the proper way to enjoy a sauna. My hope is that my musings will help you to maximize your own sauna experience.. If you follow this guide, I’m certain you will benefit from and enjoy the sauna as much as I do and, just maybe, you too will develop your own strongly held opinions that will most definitely offend me.
### Thanks for reading, please close the F-ing door.
ps, you can get a Bitcoin Honey Badger Sauna Hat [here](https://store.coinkite.com/store/ht-sauna)
- EOF
-

@ eac63075:b4988b48
2024-10-10 18:12:38
Companies like Meta (formerly Facebook) and Twitter (now X) control platforms that have become the main channels of communication for millions of people worldwide. At the center of this discussion are figures like Mark Zuckerberg and Elon Musk, whose recent actions raise serious questions about freedom of speech, censorship, and political manipulation.
---
<https://fountain.fm/episode/VzJItfySZ8z6417prHyD>
---
Recently, a public letter written by Mark Zuckerberg revealed how the U.S. government, under Joe Biden’s administration, pressured Facebook to censor information during the COVID-19 pandemic. The controversy involves, among other topics, the censorship of content related to Biden’s son, Hunter Biden, during the height of the laptop scandal. This revelation raises questions about the role these platforms play in spreading or withholding information, as well as the direct impact this has on democracy.
## **Meta and Censorship: Zuckerberg's Letter**
In his letter, Zuckerberg admitted that Facebook was pressured by the Biden administration to suppress information about the pandemic and the Hunter Biden case, something he now claims to regret. This has sparked heated debate about how far social media should go in yielding to governmental pressure. Many see this as a threat to freedom of speech, while others argue that this censorship was necessary to control misinformation.
The issue here is not just about government pressure, but the fact that Facebook, as a global platform with billions of users, holds unparalleled power to shape narratives. When a platform decides what is “acceptable” or “truthful,” it directly influences public perception and opinion formation, especially during critical moments like an election.
Zuckerberg, in his letter, seems to be trying to salvage his image, but the damage has already been done. The admission that Facebook collaborated with the government to suppress certain information raises doubts about the platform’s impartiality and its commitment to free speech.
## **Elon Musk and Free Speech on X**
Meanwhile, Elon Musk, now in control of Twitter, renamed X, has promised to transform the platform into a space for free expression. However, the reality seems more complex. Musk claims that X should be a place where all voices can be heard, regardless of political or ideological alignment. Yet, this promise has proven difficult to fulfill in practice.
X continues to ban users and censor content, especially in countries with authoritarian governments like India and Turkey. This creates a dichotomy: on the one hand, Musk advocates for unrestricted free speech, but on the other, he complies with censorship requests from these regimes. This raises questions about Musk’s true intentions and the extent to which he is willing to uphold his principles when the platform faces international pressure.
Moreover, Musk has used X as a political platform, especially in support of former President Donald Trump. The reinstatement of Trump’s account, banned during the Capitol insurrection, has raised further suspicions that Musk is turning X into a tool of political power. For many, this represents a significant risk to the neutrality of digital platforms.
## **The Cambridge Analytica Scandal and the Risk of Political Manipulation**
The discussion of censorship and free speech on social media brings up a case that shocked the world a few years ago: the Cambridge Analytica scandal. In 2015, this British company was accused of using personal data from millions of Facebook users to manipulate elections, including the Brexit referendum and Donald Trump’s 2016 presidential election.
Although Cambridge Analytica was dissolved after the scandal, its legacy remains. Big Tech companies still have access to vast amounts of user data, and the power this grants them is alarming. Companies like Meta and X could, in theory, directly influence election outcomes by manipulating algorithms to promote certain narratives or suppress others.
This scenario raises crucial questions: to what extent can we trust these platforms to act impartially? Are they truly committed to free speech, or are they using their power to shape the political future of the world according to their own interests?
## **The Pablo Marçal Case and Manipulation in Brazil**
In Brazil, a recent example that illustrates the complexity of the relationship between social media and political power is the case of coach Pablo Marçal. Marçal, who built a considerable following, became involved in controversies related to using his influence to manipulate public opinion. Recently, it was revealed that X hired the renowned law firm Pinheiro Neto to defend Marçal’s continued presence on the platform, even after controversies.
This move raises concerns about the selective enforcement of social media’s own rules. Why are some influencers protected while others are summarily banned? Marçal’s influence, particularly among conservative voters in Brazil, is undeniable, and the public defense of his account on X suggests that more is at stake than just free speech.
## **The Future of Social Media and Democracy**
What we are witnessing is the rise of a new era where social media plays a central role in global politics. Control over the flow of information lies in the hands of a few giant companies, and the decisions of their leaders—whether Mark Zuckerberg, Elon Musk, or others—can have a profound impact on elections, governments, and democracies.
This raises legitimate concerns about the future of democracy in a world where private platforms have the power to control public discourse. Big Tech censorship, often disguised as “misinformation control,” can easily become a tool for manipulation.
For citizens, this means being vigilant and critical about the information they receive on social media. Freedom of expression must be defended, but we also need to question who is behind these platforms and what their true motivations are. Trust in social media is at stake, and the future of democracy may depend on how we decide to deal with this unprecedented power.
## **Conclusion**
Recent revelations about Zuckerberg’s involvement in censorship and Musk’s use of X to promote a political agenda highlight the urgent need for transparency in social media platforms. As these companies become increasingly influential in the global political arena, the public must be aware of the risks and actively engage in the debate about the future of free speech and democracy.
-

@ c69b71dc:426ba763
2024-10-10 09:05:29
## Chef's notes
This cashew blue cheese is a true plant-based delight, delivering the rich, tangy flavours you’d expect from traditional blue cheeses like Roquefort or Gorgonzola. The fermentation process, with the help of «Penicillium Roqueforti», creates a beautifully marbled, creamy cheese that’s both bold and complex. It’s a labor of love that rewards your patience with an unforgettable vegan cheese experience! Whether enjoyed on crackers, in salads, or simply on its own, this cheese will elevate any dish with its unique flavour profile.
Note 1: For this recipe you need parchment paper, a potent blender, glass jars with lid and two cheesecloths.
Note 2: Always use very clean tools, and avoid touching with your fingers or tasting with them while working on the cheese!
## Details
- ⏲️ Prep time: 4-5 weeks
- 🍳 Cook time: 0
- 🍽️ Servings: Two small cheese loaves (2x 10-12 cm diameter)
## Ingredients
- 300g raw cashews
- 3 tbsp water
- 3 tbsp kefir, kombucha or rejuvelac
- 2 tbsp coconut oil (raw, unrefined)
- 1-4 capsules vegan probiotics
- 1/2 tsp Himalayan salt (iodine-free, no additives)
- 1/16 tsp «Penicillium Roqueforti» (blue cheese mold culture)
## Directions
1. Day 1: Soak 300g of cashews overnight in water.
2. Day 2: Rinse the soaked cashews thoroughly and let them drain well.
3. In a high-speed blender, combine the cashews, 3 tbsp of water, 3 tbsp kefir or rejuvelac, and 2 tbsp coconut oil. Blend until the mixture is smooth and creamy.
4. Add 1-4 capsules of vegan probiotics, 1/2 tsp Himalayan salt (free of iodine and additives), and blend again briefly.
5. Add a pinch (about 1/16 tsp) of «Penicillium Roqueforti» powder (blue cheese culture) and give it another quick mix.
6. Transfer the cashew mixture to a glass container, leaving the lid lightly on top (do not seal it completely) and store in a warm place, ideally in your kitchen, for 24 hours to ferment.
7. Day 3: Divide the fermented cashew mixture into two smaller glass containers lined with cheesecloth. Press the mixture down firmly to eliminate air pockets.
8. Store in a cool place (12-14°C / 53-57°F), ideally in a wine fridge.
9. Day 4: Remove the cheese from the containers, take off the cheesecloth, and turn the cheese onto parchment paper.
10. Sprinkle salt all over the cheese, ensuring it is evenly coated.
11. Cover the cheese with larger glass bowls, ensuring that air can flow from underneath, and return to the wine fridge or the cool storage area.
12. Days 4-7: Turn the cheese daily onto fresh parchment paper to maintain its texture.
13. Day 7 or 8: Pierce the cheese with a thicker wooden skewer to create holes, allowing oxygen to reach the center, encouraging the blue mold to grow throughout the cheese, not just on the surface.
14. Alternatively, crumble the cheese completely and then press it back into shape to ensure oxygen distribution.
15. Days 8 toaround 12 or 15: Once the blue mold has fully developed around and inside the cheese, wrap the cheese in parchment paper, place it in a wooden cheese box, and then wrap it in a cloth bag.
16. Transfer to a regular fridge to age for another 2-3 weeks or even several months, depending on your desired strength of flavour.
-

@ aa8de34f:a6ffe696
2024-10-09 21:56:39
\`\`\`
Technion - Israel Institute of Technology\
Foundations of Quantum Mechanics\
Date: 2024-08-25 Submitted by: Max Peter
\`\`\`
\# Quantum Mechanics and Consciousness: Strange Bedfellows
*"Does consciousness play a special role in quantum mechanics?"*
## Abstract
Could there be a connection between quantum mechanics and consciousness? This Question has fascinated scholars for years. Some believe that consciousness plays a role in how we interpret quantum theory. This essay explores whether consciousness is a fundamental component of quantum mechanics, addressing both the "hard problem" of consciousness and the various interpretations of quantum theory. By critically analyzing arguments from prominent figures like David Chalmers and Barry Loewer, the essay argues that while consciousness presents a significant challenge in understanding reality, current quantum theories may not provide the final answers. Instead, the *"hard problem"* of consciousness could be the unresolved issue that quantum mechanics needs to address, making it the *"elephant in the room"* that scientists often avoid.
## 1. Introduction
The relationship between quantum mechanics and consciousness is one of the most intriguing and contentious debates in modern science and philosophy. Quantum mechanics, the physics of the very small, has upended our classical understanding of the universe, introducing phenomena such as superposition, entanglement, and wavefunction collapse that defy intuition. Simultaneously, consciousness - the subjective experience of being aware - remains one of the most profound mysteries in science, famously described by David Chalmers (1995) as the "hard problem." The intersection of these two enigmatic fields has led to the proposal that consciousness may play a special role in quantum mechanics, particularly in the process of wavefunction collapse, where observation seems to determine physical reality. This essay explores the question: Does consciousness play a special role in quantum mechanics?
Advocates of this idea, such as Wigner and Stapp, have argued that consciousness is not merely an observer in quantum mechanics but an active participant that influences quantum events. However, this view is not without its critics. Many physicists and philosophers, including Barry Loewer, argue that connecting consciousness to quantum mechanics is speculative and unsupported by empirical evidence. Despite these criticisms, the possibility that consciousness could be the "elephant in the room" that quantum mechanics needs to address remains an open question. This essay will explore the various interpretations of quantum mechanics that engage with or avoid the issue of consciousness and will argue that the hard problem of consciousness is maybe a vital, yet often ignored, aspect of a better understanding of quantum physics.
## 2. The Basics of Quantum Mechanics
Quantum mechanics is the branch of physics that deals with the behavior of particles at the smallest scale - atoms and subatomic particles. It is governed by principles that are vastly different from the deterministic laws of classical physics. One of the foundational concepts of quantum mechanics is the wavefunction, a mathematical function that describes the probabilities of a particle's properties, such as position and momentum. Unlike in classical mechanics, where a particle has a definite position and momentum, in quantum mechanics, these properties are described by a probability distribution.
One of the most famous principles of quantum mechanics is superposition, which states that a particle can exist in multiple states simultaneously until it is observed. This is famously illustrated by Schrödinger's cat thought experiment, where a cat in a box is simultaneously alive and dead until the box is opened, and an observation is made. Another critical concept is entanglement, where particles become linked, so the state of one particle instantaneously affects the state of another, regardless of the distance between them.
The wavefunction collapse is perhaps the most perplexing aspect of quantum mechanics. When a quantum system is observed, the wavefunction collapses, and the system settles into a definite state. This raises the question: What causes the wavefunction to collapse? Is it the act of measurement itself, or does consciousness play a role in this process? The measurement problem in quantum mechanics has led some to propose that consciousness is necessary for wavefunction collapse, thus connecting the two fields in a profound way.
## 3. The Hard Problem of Consciousness
David Chalmers (1995) famously distinguished between the "easy" and "hard" problems of consciousness. The easy problems involve explaining the cognitive functions and processes that underlie perception, memory, and behavior. These problems, while challenging, are considered solvable through the standard methods of cognitive science and neuroscience. The hard problem, on the other hand, is the problem of subjective experience - why and how physical processes in the brain give rise to the rich inner life of sensation, emotion, and awareness. This subjective aspect of consciousness, also known as qualia (Latin “of what sort”), remains resistant to reductive explanation.
Chalmers (1995) argues that the hard problem of consciousness cannot be solved by merely explaining the functions of the brain. There is a gap between physical processes and the experience of those processes - a gap that traditional science struggles to bridge. This has led some theorists to propose that consciousness might be fundamental to the universe, rather than a byproduct of physical processes. This idea has significant implications for quantum mechanics, particularly in the context of the measurement problem. If consciousness is indeed fundamental, it may play a direct role in the collapse of the wavefunction, linking the hard problem of consciousness with the mysteries of quantum mechanics.
## 4. Consciousness and Quantum Mechanics
The idea that consciousness plays a special role in quantum mechanics is most closely associated with the Consciousness Collapse Proposal (CCP). This theory suggests that the act of observation by a conscious being is what causes the wavefunction to collapse into a definite state. This view was championed by physicists like Eugene Wigner and Henry Stapp, who argued that consciousness must be integrated into our understanding of quantum mechanics. According to Wigner, consciousness is the ultimate cause of the wavefunction collapse, implying that the physical world does not exist in a definite state until it is observed by a conscious mind (Wigner, 1967).
However, the CCP is not without its critics. Barry Loewer (2003) argues that the connection between consciousness and quantum mechanics is speculative and lacks empirical support. He contends that while quantum mechanics may involve strange and counterintuitive phenomena, there is no evidence that consciousness plays a direct role in these processes. Loewer suggests that alternative interpretations of quantum mechanics, such as the Ghirardi-Rimini-Weber (GRW) theory and Bohmian mechanics, offer explanations for wavefunction collapse that do not require the involvement of consciousness (Loewer, 2003).
Despite these criticisms, the idea that consciousness could be fundamental to quantum mechanics remains a compelling possibility. The CCP aligns with the notion that consciousness is not just an epiphenomenon of brain activity but a fundamental aspect of reality. This perspective challenges the materialist view that physical processes alone are sufficient to explain all phenomena, including consciousness. Instead, it suggests that consciousness might be the key to resolving the mysteries of quantum mechanics.
## 5. The Elephant in the Room: The Hard Problem of Consciousness in Quantum Mechanics
The central thesis of this section is that the hard problem of consciousness, as articulated by David Chalmers (1995), represents an unresolved issue in the interpretation of quantum mechanics, and may be the "elephant in the room" that most scientific theories attempt to avoid. While many physicists adopt materialist interpretations of quantum mechanics that sidestep the issue of consciousness, it is increasingly difficult to ignore the possibility that consciousness might play a fundamental role in the behaviour of quantum systems. This section will argue that the hard problem of consciousness is not just a philosophical curiosity but a crucial component in understanding the true nature of quantum mechanics.
### Consciousness as a Fundamental Aspect of Reality
The hard problem of consciousness refers to the challenge of explaining how and why physical processes in the brain give rise to subjective experience—what it feels like to perceive, think, and be aware. Chalmers (1995) argues that the hard problem is distinct from the "easy" problems of explaining cognitive functions and behaviours because it involves the subjective nature of experience, which cannot be fully captured by a purely physical explanation. This problem is central to the question of whether consciousness plays a role in quantum mechanics because it challenges the materialist assumption that everything can be explained in terms of physical processes.
One argument in favour of consciousness playing a fundamental role in quantum mechanics is that it may help solve the measurement problem—the question of why and how the wavefunction collapses when a measurement is made. According to the Consciousness Collapse Proposal (CCP), the collapse of the wavefunction occurs when a conscious observer interacts with the system, suggesting that consciousness is a necessary component of reality. This idea challenges the traditional view of quantum mechanics as a purely objective, observer-independent theory and implies that consciousness is more than just a byproduct of physical processes (Stapp, 1993).
In this view, consciousness is not simply an epiphenomenon of the brain but a fundamental aspect of reality that interacts with the physical world in a way that science has yet to fully understand. This perspective aligns with certain interpretations of quantum mechanics, such as the von Neumann-Wigner interpretation, which posits that consciousness plays an active role in the collapse of the wavefunction. While this interpretation remains controversial, it highlights the possibility that consciousness could be integral to the functioning of the universe at a fundamental level.
### Avoidance of the Hard Problem in Mainstream Science
Despite the compelling nature of the hard problem, mainstream scientific interpretations of quantum mechanics often avoid addressing consciousness directly. For example, the Many Worlds Interpretation (MWI) of quantum mechanics sidesteps the issue of wavefunction collapse altogether by proposing that all possible outcomes of a quantum measurement exist simultaneously in parallel worlds. In this framework, there is no need to invoke consciousness as a factor in determining the outcome of a quantum event, as every possible outcome is realized in some branch of the multiverse (Everett, 1957). While MWI elegantly avoids the problem of collapse, it does so at the cost of ignoring the role of consciousness, which remains unexplained.
Similarly, the Ghirardi-Rimini-Weber (GRW) theory offers an objective collapse model that introduces spontaneous collapses of the wavefunction, independent of observation or consciousness. This theory attempts to solve the measurement problem without invoking consciousness by suggesting that wavefunctions collapse randomly after a certain threshold is reached (Ghirardi, Rimini, & Weber, 1986). Although GRW provides a mathematically consistent solution to the measurement problem, it does not address the hard problem of consciousness, leaving the nature of subjective experience untouched.
These interpretations reflect a broader tendency in science to focus on solving the technical aspects of quantum mechanics while avoiding the deeper philosophical questions about consciousness. This approach is understandable, given that the hard problem of consciousness is notoriously difficult to address within the framework of materialist science. However, by sidestepping the issue, these interpretations may be missing a crucial piece of the puzzle. If consciousness is indeed fundamental to the collapse of the wavefunction, as proponents of the CCP suggest, then any interpretation that ignores consciousness is inherently incomplete.
### The Case for Addressing Consciousness in Quantum Mechanics
Given the limitations of current interpretations of quantum mechanics, there is a strong case to be made for addressing the hard problem of consciousness directly. One of the key challenges in integrating consciousness into quantum mechanics is the lack of empirical evidence linking consciousness to wavefunction collapse. Critics like Barry Loewer (2003) argue that the CCP is speculative and lacks the rigorous experimental support needed to be taken seriously as a scientific theory. This criticism is valid, as science requires empirical validation to support theoretical claims.
However, the absence of empirical evidence does not necessarily invalidate the idea that consciousness could play a role in quantum mechanics. The lack of direct evidence may simply reflect the limitations of current experimental methods, which are not yet sophisticated enough to test the relationship between consciousness and quantum phenomena. Furthermore, the hard problem of consciousness remains unresolved by conventional science, suggesting that new approaches may be needed to explore the connection between consciousness and the physical world.
In response to critics, proponents of the CCP could argue that quantum mechanics itself has a long history of challenging conventional notions of reality. The very existence of phenomena like entanglement and superposition defies classical logic and suggests that our understanding of the universe is incomplete. If consciousness is indeed fundamental to the fabric of reality, then it is possible that it plays a role in these quantum phenomena in ways that we do not yet fully understand. Rather than dismissing the CCP as speculative, it may be more productive to consider it as a potential avenue for further research, one that could ultimately lead to a deeper understanding of both consciousness and quantum mechanics.
## 6. Personal Viewpoint: Consciousness as a Vital Component in Quantum Mechanics
In my view, the hard problem of consciousness is not just an interesting philosophical challenge but a vital issue that must be addressed if we are to fully understand quantum mechanics. The reluctance of many scientists to engage with the hard problem is understandable, given the difficulty of the question and the lack of empirical evidence. However, this avoidance may be preventing us from making significant progress in understanding the true nature of reality.
I believe that the hard problem of consciousness represents a fundamental gap in our understanding of the universe - one that cannot be ignored if we are to develop a complete theory of quantum mechanics. While alternative interpretations like the GRW theory and the Many Worlds Interpretation offer solutions to the technical problems of quantum mechanics, they do so by avoiding the deeper question of consciousness. This approach, while pragmatic, may ultimately prove to be a dead end if consciousness is indeed integral to the behaviour of quantum systems.
Addressing the hard problem of consciousness in the context of quantum mechanics requires a willingness to think beyond the current boundaries of science and to explore new theoretical frameworks that integrate consciousness into our understanding of the physical world. This may involve revisiting ideas like the Consciousness Collapse Proposal or developing entirely new theories that link consciousness with quantum phenomena in ways that we have not yet imagined.
At the same time, it is important to approach this question with a critical and balanced perspective. While the idea that consciousness plays a role in quantum mechanics is intriguing, it is essential to remain open to alternative explanations and to demand rigorous empirical evidence to support any claims. The history of science is filled with theories that seemed promising but ultimately proved to be incorrect, and we must be careful not to fall into the trap of speculation without evidence.
## Conclusion
In Summary, I believe that the hard problem of consciousness is the *"elephant in the room"* that quantum mechanics needs to address. While traditional interpretations of quantum theory have tried to solve the measurement problem without involving consciousness it might be ignoring a part of reality.
By blending the matter of consciousness into quantum mechanics we could potentially gain a comprehensive view of the universe - one that appreciates both the enigmatic nature of subjective experiences and the elegant mathematics of some quantum mechanics theories. Even though this viewpoint is speculative and needs investigation it presents a glimpse into a future where consciousness and quantum mechanics are seen as interconnected elements of existence.
### References
\- CHALMERS, D. J. (1995). FACING UP TO THE PROBLEM OF CONSCIOUSNESS. JOURNAL OF CONSCIOUSNESS STUDIES, 2(3), 200-219.
\- EVERETT, H. (1957). “RELATIVE STATE” FORMULATION OF QUANTUM MECHANICS. REVIEWS OF MODERN PHYSICS, 29(3), 454-462.
\- GHIRARDI, G. C., RIMINI, A., & WEBER, T. (1986). UNIFIED DYNAMICS FOR MICROSCOPIC AND MACROSCOPIC SYSTEMS. PHYSICAL REVIEW D, 34(2), 470-491.
\- LOEWER, B. (2003). CONSCIOUSNESS AND QUANTUM THEORY: STRANGE BEDFELLOWS.
\- STAPP, H. P. (1993). MIND, MATTER, AND QUANTUM MECHANICS. SPRINGER.
-

@ 4ba8e86d:89d32de4
2024-10-08 23:16:53
Governos do mundo industrial, seus gigantes cansados de carne e aço, venho do ciberespaço, a nova casa da mente. Em nome do futuro, peço que no passado nos deixe em paz. Você não é bem vindo entre nós. Nem você exerce qualquer soberania sobre o lugar onde nos encontramos. Não elegemos nenhum governo, nem pretendemos tê-lo, por isso dirijo-me a vocês sem outra autoridade senão aquela com que sempre fala a liberdade.
Declaro que o espaço social global que estamos construindo é independente por natureza das tiranias que você procura impor a nós. Você não tem o direito moral de nos governar, nem possui métodos para fazer cumprir sua lei que devemos realmente temer.
Os governos obtêm seus justos poderes do consentimento daqueles que são governados. Você não pediu nem recebeu o nosso. Nós também não convidamos você.
Você não nos conhece, nem conhece o nosso mundo. O ciberespaço não está dentro de suas fronteiras. Não pense que você pode construí-lo, como se fosse um projeto de construção pública. Você não pode. É um ato natural que cresce a partir de nossas ações coletivas.
Você não participou de nossa grande conversa coletiva, nem criou a riqueza de nossos mercados. Você não conhece nossa cultura, nossa ética ou os códigos não escritos que já fornecem à nossa sociedade mais ordem do que o que poderia ser obtido por qualquer uma de suas imposições.
Você proclama que há problemas entre nós que precisa resolver. Você usa isso como uma desculpa para invadir nossos limites. Muitos desses problemas não existem. Onde houver conflitos reais, erros, nós os identificaremos e resolveremos por nossos próprios meios. Estamos criando nosso próprio contrato social. Essa autoridade será criada de acordo com as condições do nosso mundo, não a sua. Nosso mundo é diferente. O ciberespaço é composto de transações, relacionamentos e pensamento em si, que se espalham como uma onda silenciosa na web de nossas comunicações. Nosso mundo está ao mesmo tempo em todo lugar e lugar nenhum, mas não é onde os corpos vivem.
Estamos criando um mundo no qual todos possam entrar, sem privilégios ou preconceitos devido à raça, poder econômico, força militar ou local de nascimento.
Estamos criando um mundo em que qualquer pessoa, em qualquer lugar, possa expressar suas crenças, não importa quão únicas sejam, sem medo de ser coagida ao silêncio ou à conformidade.
Seus conceitos legais de propriedade, expressão, identidade, movimento e contexto não se aplicam a nós. Eles são baseados na matéria.
Não há problema aqui. Nossas identidades não têm corpo; portanto, diferentemente de você, não podemos obter ordem por coerção física.
Acreditamos que nossa autoridade emanará da moralidade, do interesse próprio progressivo e do bem comum. Nossas identidades podem ser distribuídas por várias jurisdições. A única lei que todas as nossas culturas reconheceriam é a Regra de Ouro. Esperamos ansiosamente desenvolver nossas soluções específicas sobre essa base. Mas não podemos aceitar as soluções que você está tentando impor. Hoje, na América, você criou uma lei, a Lei de Reforma das Telecomunicações, que repudia sua própria Constituição e insulta os sonhos de Jefferson, Washington, Mill, Madison, DeToqueville e Brandeis. Esses sonhos devem renascer em nós agora.
Você tem medo de seus próprios filhos, pois eles são nativos em um mundo onde você sempre será imigrante. Ao recear, confia à sua burocracia responsabilidades parentais que não pode ser covarde. Em nosso mundo, todos os sentimentos e expressões da humanidade, do mais vil ao mais angélico, fazem parte de um único todo, a conversa global de bits. Não podemos separar o ar que sufoca daquele em que as asas batem.
Na China, Alemanha, França, Rússia, Cingapura, Itália e Estados Unidos, você está tentando evitar o vírus da liberdade, estabelecendo postos de guarda nas fronteiras do ciberespaço. Eles podem impedir o contágio por um curto período de tempo, mas não funcionarão em um mundo que em breve será coberto pela mídia transmitida por bits.
Suas indústrias de informação cada vez mais obsoletas se perpetuariam propondo leis, nos Estados Unidos e em outros lugares, que reivindicam a propriedade da palavra em todo o mundo. Essas leis declarariam que as idéias são outro produto industrial, menos nobre que o ferro enferrujado. Em nosso mundo, tudo o que a mente humana pode criar pode ser reproduzido e distribuído infinitamente, sem nenhum custo. A transferência global de pensamento não precisa mais ser realizada por suas fábricas. Essas medidas cada vez mais hostis e colonialistas nos colocam na mesma situação em que estavam aqueles amantes da liberdade e da autodeterminação que tiveram que lutar contra a autoridade de um poder distante e ignorante.
Devemos declarar nossos "eus" virtuais imunes à sua soberania, embora continuemos a consentir com seu poder sobre nossos corpos. Vamos nos espalhar por todo o planeta para que ninguém possa aprisionar nossos pensamentos.
Criaremos uma civilização da mente no ciberespaço. Que seja mais humano e bonito do que o mundo que seus governos criaram antes.
Davos, Suíça, até 8 de fevereiro de 1996
John Perry Barlow
-

@ eac63075:b4988b48
2024-10-08 20:37:08
In this botcast, we explore how technology is solving one of the biggest challenges faced by DAOs (Decentralized Autonomous Organizations): vote fraud. Learn how Vitalik Buterin and other experts from Cornell University are leading innovation using Zero-Knowledge Proofs and Proof of Work (PoW) to ensure security and privacy in blockchain voting systems.
You will discover how these technologies combat practices like token renting and lending, preventing vote manipulation in DAOs. The video also covers the importance of dedicated hardware to increase the integrity of digital elections.
---
Listen to the Podcast:
<https://wavlake.com/episode/bdb2850b-49b4-45f6-9a00-d310e29f4528>
---
Table of Contents:
**Source:** YouTube Transcript - Morning Crypto (Timestamped Excerpts)
**I. Introduction and Context (0:00:00 - 0:02:37)**
- This section sets the stage by briefly discussing a common problem in Decentralized Autonomous Organizations (DAOs): fraudulent voting practices.
- It highlights the issue of individuals manipulating voting systems by borrowing, renting, or delegating tokens to influence decision-making within DAOs.
**II. Introducing Complete Knowledge and the Proposed Solution (0:02:37 - 0:03:39)**
- Introduces a potential solution developed by Vitalik Buterin and researchers from Cornell University, utilizing Zero-Knowledge Proofs to address the challenge of fraudulent voting in DAOs.
- Explains that the proposed solution involves a dedicated hardware or wallet system that verifies voting rights without revealing the user's private key, preventing token manipulation.
**III. Deep Dive into Complete Knowledge with "Ger" (0:05:54 - 0:07:57)**
- This section features "Ger," a voice assistant, who explains Complete Knowledge as a cryptographic innovation.
- Ger describes how Complete Knowledge allows users to prove possession of information, like a private key, without revealing the information itself.
- The section emphasizes how Complete Knowledge enhances security and privacy in digital identity and voting systems.
**IV. Proof of Work and ASICs for Enhanced Security (0:07:57 - 0:09:05)**
- Examines the potential of using Proof of Work (PoW), the consensus mechanism behind Bitcoin, in conjunction with Complete Knowledge.
- Explains how PoW can act as a mechanism to further ensure that a specific secret or key is held by a user without requiring the user to reveal it.
- Discusses the use of Application-Specific Integrated Circuits (ASICs) for performing the computational tasks required for PoW and Complete Knowledge verification.
**V. Practical Implementation and Conclusion (0:09:05 - 0:10:25)**
- Highlights the development of a demo ASIC by the researchers, showcasing the practical application of their proposed solution.
- Emphasizes the potential of this technology to prevent fraudulent voting practices by requiring a user to generate proof of their voting rights via this specialized ASIC.
- Concludes with a message emphasizing the importance of verifiable knowledge and its implications for privacy and security in the digital age.
---
Reference:
- <https://eprint.iacr.org/2023/044>
- <https://medium.com/initc3org/complete-knowledge-eecdda172a81>
-

@ 1bda7e1f:bb97c4d9
2024-10-08 09:46:01
**Tldr**
- Nostr comes with integrated Bitcoin payments called zaps
- It’s possible to set up a self-custodial wallet that you host yourself, plus
- Add all kinds of bells and whistles, like phone app and browser plugin
- The software I’m using is Albyhub and Phoenixd, deployed with Docker to a cheap VPS
- I can now receive payments to my Lightning Address rodbishop@getalby.com
**Payments on Nostr**
One of the great features of Nostr is integrated payments. This feature integrates financial transactions directly into the social network, as a seamless part of using the network.
You can get paid by and pay anyone on the network, to or from anywhere in the world, and for any reason, in a way that is instant and nearly free.
The payments get to be instant and global and free because they are made in Bitcoin, using the Bitcoin payments network called The Lightning Network.
Per Bitcoin, payments are denominated in satoshis (sats). A sat is a one-hundred-millionth of a Bitcoin– US$1 is about 1,700 sats at the time of writing. Making a payment like this on Nostr is called a “zap” and usually indicated with a lightning bolt symbol (you are getting “zapped by lightning”). You might say to your friend ”I'll zap you 1,700 sats”.
This unlocks all kinds of interesting things that are not possible with other social networks, like
- “value for value”–A publisher publishes something of value and you can tip them if you like it
- Payments between friends–Nostr can do everything that Cash App and Venmo can do, right down to splitting payments to multiple recipients
- Payments for creators–you can sell or pay to access premium content similar to any kind of paywall site like Patreon or Substack
- Payments to AIs–you can pay for automated AI-based services including for translation, image generation, or creating custom curated social media feeds
- All other kinds of ecommerce–you can sell or buy anything you want similar to Gumtree or Facebook marketplace
Every Nostr user can have this set up. It's free or nearly free to set up, nearly free to make payments, and some apps like Primal will even set it up for you by default.
Moreover it's useful and it's fun.
- When you help someone out to receive a little tip for doing so, or
- When you get some great advice to show your appreciation in a more meaningful way than a like
**Ways to set up lightning for zaps on Nostr**
You can get paid in Bitcoin to a lightning address. This looks exactly like an email address except you can make a payment to it from a lightning wallet.
Anyone can publish their lightning address on Nostr so that you can pay them. And you can also get your own lightning address on your own Nostr profile so that people can pay you.
The lightning address links to a server that’s always active and ready to credit your balance whenever you receive payments.
To make that happen at a high level there are two options, either:
- Open an account with a custodial lightning provider who will keep an always on server with your wallet on it, live and ready to receive payments for you. Primal does this automatically for you in their Nostr client, or you can use any one of the other popular custodial wallets like Wallet of Satoshi, Zeus, Coinos, or many others
- Set up your own self-custodial lightning server that runs on an always-on computer or server, which you can administer yourself
Generally using a custodial service will be easier, but comes with the need to trust that third party custodian, and may limit you to pay within their app.
For myself I'm going to self host using Albyhub by npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm, and Phoenixd by Acinq.
**Hosting your own lightning server with Albyhub and Phoenixd**
Anyone who's experimented with self-sovereign setups for Bitcoin know that historically there's been quite a bit of heavy lifting.
My number one favourite feature of what Albyhub and Phoenixd have done together is to create a nearly instant set up with no heavy lifting. I was stunned. For anyone who's used to jumping through hoops with this, it was like magic.
You can use Albyhub with any lightning wallet backend, but in my view none are as automatic, and magic, as Phoenixd.
Compare the traditional set up with the Albyhub and Phoenixd setup.
Traditional–
- Set up a Bitcoin core node
- Download the entire Bitcoin blockchain (wait several days for it to download)
- Set up a Bitcoin lightning node
- Purchase payment liquidity to enable payments to the network
- On an ongoing basis continue to keep your blockchain in sync with the network
- On an ongoing basis manage your inbound and outbound liquidity to your network peers
Vs Albyhub and Phoenixd–
- No Bitcoin core
- No initial block download
- Phoenixd provides liquidity for you automatically and by default
- Nothing to keep in sync with the network
- No liquidity to manage
For any normal non-technical user, self-hosting your own lightning node just went from being too hard, to very achievable.
**Unpacking the parts**
There are a few parts to this set up and there’s a bit of assumed knowledge here, so let’s quickly unpack it
- Bitcoin–money for the internet, which enables payments to and from anywhere
- Lightning–the main payments network that sits on top of Bitcoin, which makes transactions instantly and with very low fees
- Phoenixd–a lightning wallet back-end with special methods for managing liquidity that makes it almost no-touch to set up and manage
- Albyhub–a lightning front-end with an easy to-use wallet, and a feature called “Nostr Wallet Connect” (NWC) which connects the wallet to Nostr
- AlbyGo–a phone app so you can make payments on your phone
- Alby Plugin–a web browser plugin so you can make payments on your browser, and also log into Nostr from your browser (using NIP-07)
- NWC–a method for connecting your wallet directly to Nostr apps so that you can spend from your wallet balance without even leaving the app
- Lightning Address–an address like an email address where you can receive payments (using LNURLp; Lightning Network URL)
I'm going to plug it all together, so that I can pay for anything in any way I like (from NWC, Alby Plugin or Alby Go), and receive payment from anyone (to our Lightning Address), with all funds managed on my own server (hosting Albyhub and Phoenixd).
**How to set up Albyhub and Phoenixd**
To set this up requires basic command line knowledge, and some experience with Docker. I didn’t have that experience, so I gave ChatGPT the docs on each of Albyhub and Phoenixd and it walked me through the setup.
To start with, I got myself a cheap VPS, and installed Docker. Docker then allowed me to deploy Albyhub and Phoenixd as a container.
The Albyhub Github contains very helpful readme, here <https://github.com/getAlby/hub>
And Phoenixds own docs here <https://phoenix.acinq.co/server> and here <https://github.com/ACINQ/phoenixd>
Alby also has a dedicated section to working with Albyhub with Phoenixd backend, here <https://github.com/getAlby/hub/blob/master/scripts/linux-x86_64/phoenixd/README.md>
First, install Docker and make sure it is running.
Then working with the code on the Albyhub with Phoenixd page–
- Get the docker-compose.yml file which will instruct Docker to create the relevant containers,
- Create the directories for the files to be stored in
- Launch the containers
That’s it. Docker will proceed to create the application for you running on port 8080
You can then log in in a web browser and start the setup–
- There’s a helpful step-by-step guide to walk you through the set up including to set up a password for your hub
- It will ask you to connect your Alby account. I skipped that step as I didn’t have one at the time, I only created one later
- If you used the default lightning back-end, Alby will then ask you to buy your first liquidity to enable you to make payments. Or, if you are using Phoenixd, then the step is automatic and you can go right ahead to transfer in some initial funds
**Setting up the bells and whistles**
That's the hard part done. The next step is add all the little extra pieces that make for a great Nostr experience.
Alby Browser Plugin–
- Download the Alby Browser Plugin to your web browser and create an account
- It will give you a new Nostr and Lightning account by default, and you can replace it
- For me I had my own keys already saved with a mnemonic backup, and I wanted to use these. I went to Settings and clicked “Remove Master Key”, then entered the mnemonic backup of my own keys. I also went to Nostr Settings and clicked “Derive from Master Key” to replace the one it generated by default.
- Visit Albyhub, and connect the Alby Account
- This completes the set up to login and zap with Nostr on any Nostr site
Alby Go App
- Download the Alby Go App to your phone from your phone’s app store
- Vist Albyhub, go to the Alby App Store, and click Alby Go
- It will help you to create a connection between your Albyhub and Alby Go
Nostr Wallet Connect
- You can use the Alby App Store to connect any Nostr app in the same way
- Vist Albyhub, go to the Alby App Store, and click on any Nostr App
- I used Amethyst, and I was able to create a connection between Amethyst Nostr app and Albyhub, so that when I click the “zap” icon in Amethyst it can automatically spend from my Albyhub wallet without any further clicks
Your own Lightning Address
- Your Alby Account in your Alby Browser Plugin gives you a Lightning Address by default. It is generated randomly to start with, and you can replace it.
- Open the Alby Browser Plugin and visit Settings
- Click “Change on [getalby.com](http://getalby.com)” and change it to something that suits you
- I changed mine to rodbishop@getalby.com
That completes the set up.
**Backups**
Now that everything is set up, it’s time to make a backup.
I already had my Nostr keys as a mnemonic backup from my last article, and I’m using these keys for my Alby Account, so there is nothing new to back up there.
But we still need backups for the Albyhub login credentials, and the Phoenixd wallet.
When started for the first time, Phoenixd will generate a 12-word mnemonic of its own, which it will use to restore your wallet balance in case of any issue. This recovery phrase is stored in the phoenix folder you created, at \~/.phoenixd/seed.dat.
In total, your backups will contain:
- Your 12 word mnemonic backup of your Nostr keys, that is also the same master 12 word mnemonic for your Alby account
- Your 12 word mnemonic backup for your Phoenixd wallet, that is created by the daemon when it first runs at \~/.phoenixd/seed.dat
- Three passwords: 1) Your password for your Alby account, 2) Your password for your Alby Hub, 3) Your password for your Phoenixd (that is hardcoded into the docker-compose.yml)
Once these are backed up somewhere safely, you can fully recover your set up if ever anything goes wrong.
**Things I did wrong in set up so that you don’t have to**
Initially I had some trouble with user permissions. I was able to resolve it by changing the user configuration in the docker-compose.yml.
I also had some trouble with the initial funds transfer. In order to test everything without risking significant funds, I made an initial transfer to the hub of 10 satoshis.
- The transfer was received immediately, but
- The available balance stayed at zero, and
- I couldn’t make any payments (insufficient funds)
I thought this was a bug in my set up, but it turns out this is a feature of Phoenixd auto-liquidity, that it keeps some initial sats as a payment credit to buy the required lightning channel liquidity. The total cost amounts to on average 1% charge, but it is also front-loaded, and because my payment was so very tiny (10 satoshis worth a fraction of a cent) the payment was entirely front-loaded.
I diagnosed this by accessing Phoenixd directly in the cli, and by doing so, I was able to see the balance present, as a fee credit.
To check, run–
- docker-compose exec albyhub-phoenixd /phoenix/bin/phoenix-cli --http-password=<your-password-here> getbalance
And receive a response like this, which shows the credit on the account –
- { "balanceSat": 0, "feeCreditSat": 10 }
The above command–
- accesses the albyhub-phoenixd container “docker-compose exec albyhub-phoenixd”,
- then accesses the phoenix-cli application at “/phoenix/bin/phoenix-cli”
- and asks the application to “getbalance”
Helpful docs–
- Phoenixd talks about that fee credit behaviour quite clearly at their own site, here <https://phoenix.acinq.co/server>
- They also provide docs on their cli to interact directly with their daemon (rather than using Alby), which you can read here <https://phoenix.acinq.co/server/get-started>
I wondered what the total initial amount would be that would be captured as fee credit. Your mileage might vary, but for me:
- I transferred in 2,100 sats (about $1.20)
- I received a working balance of 775 sats, so I paid 1,325 sats in fees
- I then transferred in another 2,100 sats
- I received all 2,100 sats (paid no fees at all on the second transaction)
All up only a few cents to get started with initial liquidity.
**In summary**
Nostr has integrated payments that are instant and nearly free, using Satoshis on the Lightning Network. Some Nostr clients come with a wallet set up automatically, and it is quite easy to set up your own self-custody wallet, with all the bells and whistles.
I wanted to set up my own self-custody wallet so that I could test and learn the full set up of the system. For this I used Albyhub and Phoenixd, and I deployed it to a cheap VPS using Docker.
Once set up, I added all the extra bits so that now–
- I can login to Nostr from my web browser with the Alby Browser Plugin
- I can make payments from there too, or from the AlbyGo App, or from any Nostr app I like
- I can receive payments to my Lightning Address [rodbishop@getalby.com](mailto:rodbishop@getalby.com)
And in doing this–
- I don’t rely on any third-party custodian to take care of my funds
- I had no hard work to install this setup, and expect no ongoing admin to keep it running
- With everything set up, the system simply works (so far!)
For anyone interested in Nostr or Bitcoin software or technologies, I recommend to go through a set up like this as it really covers the full gamut or the Nostr–Lightning–Bitcoin stack. It’s clear how far this technology has come and how powerful it can get from here.
**Up next**
- Please let me know if this kind of post is helpful or anything you’d like me to improve or expand upon
- For my next post I’ll show how I set up Nostr and lightning addresses at your own domain with Sveltekit and Vercel
-

@ 4ba8e86d:89d32de4
2024-10-06 20:26:43
O aplicativo é desenvolvido por uma comunidade de colaboradores e segue os princípios de código aberto, o que significa que o código-fonte do aplicativo é acessível e pode ser modificado por qualquer pessoa interessada em contribuir para o projeto.
O AntennaPod foi lançado pela primeira vez em 2012 como um projeto de código aberto desenvolvido por uma equipe de voluntários. A ideia por trás do aplicativo era criar uma alternativa livre e de código aberto para gerenciar e ouvir podcasts em dispositivos Android. O projeto inicialmente começou como uma bifurcação (fork) do projeto Podtrapper, um aplicativo de podcast para dispositivos BlackBerry. A equipe de desenvolvimento do AntennaPod adaptou o código do Podtrapper para o Android e adicionou novos recursos e funcionalidades. Ao longo dos anos, o AntennaPod passou por várias atualizações e melhorias, com contribuições de desenvolvedores de todo o mundo. A comunidade de código aberto em torno do AntennaPod cresceu e ajudou a moldar o aplicativo, fornecendo feedback, correções de bugs e novos recursos. O AntennaPod se tornasse uma opção flexível e personalizável para o gerenciamento de podcasts no Android. Ele foi projetado para suportar uma ampla variedade de formatos e servidores de podcast, oferecendo aos usuários a liberdade de escolher suas fontes de podcast favoritas. Ele permanece como uma opção popular para os entusiastas de podcasts que buscam uma solução livre e acessível para gerenciar e desfrutar de seu conteúdo de áudio favorito.
Aqui estão algumas das principais vantagens do AntennaPod:
1. Livre e de código aberto: O AntennaPod é um software de código aberto, o que significa que o seu código-fonte está disponível para visualização, modificação e contribuição pela comunidade de desenvolvedores. Isso proporciona transparência, segurança e a possibilidade de personalizar o aplicativo de acordo com as necessidades individuais.
2. Sem necessidade de login: Ao contrário de alguns outros aplicativos de podcast, o AntennaPod não requer um login para acessar e gerenciar seus podcasts. Isso oferece praticidade e privacidade aos usuários, pois não é necessário criar uma conta ou compartilhar informações pessoais.
3. Adição de podcasts via RSS: O AntennaPod permite que os usuários adicionem podcasts por meio de feeds RSS. Isso significa que você pode adicionar facilmente seus podcasts favoritos ao copiar e colar o link do feed RSS, sem a necessidade de procurar manualmente ou depender de uma biblioteca restrita.
4. Interface intuitiva: O aplicativo possui uma interface de usuário intuitiva e fácil de usar, com navegação simples e organizada. Isso torna a descoberta, a assinatura e a reprodução de podcasts uma experiência agradável e acessível para todos.
5. Reprodução offline: O AntennaPod permite que você faça o download de episódios de podcast para ouvir offline. Isso é especialmente útil quando você está em movimento, sem conexão à internet ou deseja economizar dados móveis. Você pode baixar seus episódios favoritos e ouvi-los em qualquer lugar, a qualquer momento.
6. Gerenciamento de listas de reprodução: O aplicativo oferece a opção de criar listas de reprodução personalizadas para organizar seus episódios de podcast. Isso permite que você crie uma sequência de reprodução personalizada, reorganize os episódios e gerencie melhor o que deseja ouvir.
7. Controles de reprodução avançados: O AntennaPod oferece uma variedade de recursos avançados de controle de reprodução, como avançar ou retroceder episódios, definir temporizadores de suspensão, pular partes silenciosas e ajustar o volume de reprodução.
8. Personalização de configurações: O aplicativo permite que você personalize várias configurações de acordo com suas preferências. Isso inclui ajustar a velocidade de reprodução dos episódios, configurar notificações, gerenciar downloads automáticos, definir limites de armazenamento e muito mais.
9. Suporte a diferentes idiomas: O AntennaPod suporta podcasts em vários idiomas, o que permite que os usuários descubram e desfrutem de conteúdos em seu idioma preferido.
10. Sincronização com serviços em nuvem: O AntennaPod oferece suporte à sincronização com serviços em nuvem, como o Nextcloud, permitindo que você sincronize seus podcasts e configurações entre vários dispositivos. Isso garante que você possa continuar de onde parou em diferentes dispositivos sem perder seu progresso.
Essas são algumas das principais vantagens do AntennaPod. O aplicativo continua sendo desenvolvido e aprimorado pela comunidade de código aberto, trazendo constantemente novos recursos e melhorias para tornar a experiência de audição de podcasts mais completa, personalizável e agradável para os usuários.
https://github.com/AntennaPod/AntennaPod
https://antennapod.org/
-

@ e6817453:b0ac3c39
2024-10-06 11:21:27
Hey folks, today we're diving into an exciting and emerging topic: personal artificial intelligence (PAI) and its connection to sovereignty, privacy, and ethics. With the rapid advancements in AI, there's a growing interest in the development of personal AI agents that can work on behalf of the user, acting autonomously and providing tailored services. However, as with any new technology, there are several critical factors that shape the future of PAI. Today, we'll explore three key pillars: privacy and ownership, explainability, and bias.
<iframe width="560" height="315" src="https://www.youtube.com/embed/fehgwnSUcqQ?si=nPK7UOFr19BT5ifm" title="YouTube video player" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen></iframe>
### 1. Privacy and Ownership: Foundations of Personal AI
At the heart of personal AI, much like self-sovereign identity (SSI), is the concept of ownership. For personal AI to be truly effective and valuable, users must own not only their data but also the computational power that drives these systems. This autonomy is essential for creating systems that respect the user's privacy and operate independently of large corporations.
In this context, privacy is more than just a feature—it's a fundamental right. Users should feel safe discussing sensitive topics with their AI, knowing that their data won’t be repurposed or misused by big tech companies. This level of control and data ownership ensures that users remain the sole beneficiaries of their information and computational resources, making privacy one of the core pillars of PAI.
### 2. Bias and Fairness: The Ethical Dilemma of LLMs
Most of today’s AI systems, including personal AI, rely heavily on large language models (LLMs). These models are trained on vast datasets that represent snapshots of the internet, but this introduces a critical ethical challenge: bias. The datasets used for training LLMs can be full of biases, misinformation, and viewpoints that may not align with a user’s personal values.
This leads to one of the major issues in AI ethics for personal AI—how do we ensure fairness and minimize bias in these systems? The training data that LLMs use can introduce perspectives that are not only unrepresentative but potentially harmful or unfair. As users of personal AI, we need systems that are free from such biases and can be tailored to our individual needs and ethical frameworks.
Unfortunately, training models that are truly unbiased and fair requires vast computational resources and significant investment. While large tech companies have the financial means to develop and train these models, individual users or smaller organizations typically do not. This limitation means that users often have to rely on pre-trained models, which may not fully align with their personal ethics or preferences. While fine-tuning models with personalized datasets can help, it's not a perfect solution, and bias remains a significant challenge.
### 3. Explainability: The Need for Transparency
One of the most frustrating aspects of modern AI is the lack of explainability. Many LLMs operate as "black boxes," meaning that while they provide answers or make decisions, it's often unclear how they arrived at those conclusions. For personal AI to be effective and trustworthy, it must be transparent. Users need to understand how the AI processes information, what data it relies on, and the reasoning behind its conclusions.
Explainability becomes even more critical when AI is used for complex decision-making, especially in areas that impact other people. If an AI is making recommendations, judgments, or decisions, it’s crucial for users to be able to trace the reasoning process behind those actions. Without this transparency, users may end up relying on AI systems that provide flawed or biased outcomes, potentially causing harm.
This lack of transparency is a major hurdle for personal AI development. Current LLMs, as mentioned earlier, are often opaque, making it difficult for users to trust their outputs fully. The explainability of AI systems will need to be improved significantly to ensure that personal AI can be trusted for important tasks.
### Addressing the Ethical Landscape of Personal AI
As personal AI systems evolve, they will increasingly shape the ethical landscape of AI. We’ve already touched on the three core pillars—privacy and ownership, bias and fairness, and explainability. But there's more to consider, especially when looking at the broader implications of personal AI development.
Most current AI models, particularly those from big tech companies like Facebook, Google, or OpenAI, are closed systems. This means they are aligned with the goals and ethical frameworks of those companies, which may not always serve the best interests of individual users. Open models, such as Meta's LLaMA, offer more flexibility and control, allowing users to customize and refine the AI to better meet their personal needs. However, the challenge remains in training these models without significant financial and technical resources.
There’s also the temptation to use uncensored models that aren’t aligned with the values of large corporations, as they provide more freedom and flexibility. But in reality, models that are entirely unfiltered may introduce harmful or unethical content. It’s often better to work with aligned models that have had some of the more problematic biases removed, even if this limits some aspects of the system’s freedom.
The future of personal AI will undoubtedly involve a deeper exploration of these ethical questions. As AI becomes more integrated into our daily lives, the need for privacy, fairness, and transparency will only grow. And while we may not yet be able to train personal AI models from scratch, we can continue to shape and refine these systems through curated datasets and ongoing development.
### Conclusion
In conclusion, personal AI represents an exciting new frontier, but one that must be navigated with care. Privacy, ownership, bias, and explainability are all essential pillars that will define the future of these systems. As we continue to develop personal AI, we must remain vigilant about the ethical challenges they pose, ensuring that they serve the best interests of users while remaining transparent, fair, and aligned with individual values.
If you have any thoughts or questions on this topic, feel free to reach out—I’d love to continue the conversation!
-

@ 63e20439:86c3c470
2024-10-06 05:35:24
What is one Satishi (sats)?
In simple terms there are 100 million satoshis (sats) in one bitcoin. Meaning each satoshi is worth 0.00000001 bitcoin. or one sats is 100 million part of each bitccoin.
If you want to shop and earn free sats
satsback.com is right place for cashback and loyalty rewards in Satoshies (sats) They work with online stores to help you save in bitcoin whenever you shop online.
As soon sats are available in your account you can instantly withdraw it to your lightning address.
-

@ 47750177:8969e41a
2024-10-05 17:40:25
28.0 Release Notes
==================
Bitcoin Core version 28.0 is now available from:
- 🌐 <https://bitcoincore.org/bin/bitcoin-core-28.0/>
- 🧲 <magnet:?xt=urn:btih:e18e92024fc9d4026cf8cdef174f03c24080fd1f&dn=bitcoin-core-28.0&tr=udp%3A%2F%2Ftracker.coppersurfer.tk%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.openbittorrent.com%3A80&tr=udp%3A%2F%2Ftracker.opentrackr.org%3A1337%2Fannounce&tr=udp%3A%2F%2Ftracker.torrent.eu.org%3A451%2Fannounce&tr=udp%3A%2F%2Ftracker.leechers-paradise.org%3A6969%2Fannounce&tr=udp%3A%2F%2Fexplodie.org%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.bitcoin.sprovoost.nl%3A6969&ws=http://bitcoincore.org/bin/>
This release includes new features, various bug fixes and performance
improvements, as well as updated translations.
Please report bugs using the issue tracker at GitHub:
<https://github.com/bitcoin/bitcoin/issues>
To receive security and update notifications, please subscribe to:
<https://bitcoincore.org/en/list/announcements/join/>
How to Upgrade
==============
If you are running an older version, shut it down. Wait until it has completely
shut down (which might take a few minutes in some cases), then run the
installer (on Windows) or just copy over `/Applications/Bitcoin-Qt` (on macOS)
or `bitcoind`/`bitcoin-qt` (on Linux).
Upgrading directly from a version of Bitcoin Core that has reached its EOL is
possible, but it might take some time if the data directory needs to be migrated. Old
wallet versions of Bitcoin Core are generally supported.
Running Bitcoin Core binaries on macOS requires self signing.
```
cd /path/to/bitcoin-28.0/bin
xattr -d com.apple.quarantine bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoin
codesign -s - bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoin
```
Compatibility
==============
Bitcoin Core is supported and extensively tested on operating systems
using the Linux Kernel 3.17+, macOS 11.0+, and Windows 7 and newer. Bitcoin
Core should also work on most other UNIX-like systems but is not as
frequently tested on them. It is not recommended to use Bitcoin Core on
unsupported systems.
Notable changes
===============
Testnet4/BIP94 support
-----
Support for Testnet4 as specified in [BIP94](https://github.com/bitcoin/bips/blob/master/bip-0094.mediawiki)
has been added. The network can be selected with the `-testnet4` option and
the section header is also named `[testnet4]`.
While the intention is to phase out support for Testnet3 in an upcoming
version, support for it is still available via the known options in this
release. (#29775)
Windows Data Directory
----------------------
The default data directory on Windows has been moved from `C:\Users\Username\AppData\Roaming\Bitcoin`
to `C:\Users\Username\AppData\Local\Bitcoin`. Bitcoin Core will check the existence
of the old directory first and continue to use that directory for backwards
compatibility if it is present. (#27064)
JSON-RPC 2.0 Support
--------------------
The JSON-RPC server now recognizes JSON-RPC 2.0 requests and responds with
strict adherence to the [specification](https://www.jsonrpc.org/specification).
See [JSON-RPC-interface.md](https://github.com/bitcoin/bitcoin/blob/master/doc/JSON-RPC-interface.md#json-rpc-11-vs-20) for details. (#27101)
JSON-RPC clients may need to be updated to be compatible with the JSON-RPC server.
Please open an issue on GitHub if any compatibility issues are found.
libbitcoinconsensus Removal
---------------------------
The libbitcoin-consensus library was deprecated in 27.0 and is now completely removed. (#29648)
P2P and Network Changes
-----------------------
- Previously if Bitcoin Core was listening for P2P connections, either using
default settings or via `bind=addr:port` it would always also bind to
`127.0.0.1:8334` to listen for Tor connections. It was not possible to switch
this off, even if the node didn't use Tor. This has been changed and now
`bind=addr:port` results in binding on `addr:port` only. The default behavior
of binding to `0.0.0.0:8333` and `127.0.0.1:8334` has not been changed.
If you are using a `bind=...` configuration without `bind=...=onion` and rely
on the previous implied behavior to accept incoming Tor connections at
`127.0.0.1:8334`, you need to now make this explicit by using
`bind=... bind=127.0.0.1:8334=onion`. (#22729)
- Bitcoin Core will now fail to start up if any of its P2P binds fail, rather
than the previous behaviour where it would only abort startup if all P2P
binds had failed. (#22729)
- UNIX domain sockets can now be used for proxy connections. Set `-onion` or `-proxy`
to the local socket path with the prefix `unix:` (e.g. `-onion=unix:/home/me/torsocket`).
(#27375)
- UNIX socket paths are now accepted for `-zmqpubrawblock` and `-zmqpubrawtx` with
the format `-zmqpubrawtx=unix:/path/to/file` (#27679)
- Additional "in" and "out" flags have been added to `-whitelist` to control whether
permissions apply to inbound connections and/or manual ones (default: inbound only). (#27114)
- Transactions having a feerate that is too low will be opportunistically paired with
their child transactions and submitted as a package, thus enabling the node to download
1-parent-1-child packages using the existing transaction relay protocol. Combined with
other mempool policies, this change allows limited "package relay" when a parent transaction
is below the mempool minimum feerate. Topologically Restricted Until Confirmation (TRUC)
parents are additionally allowed to be below the minimum relay feerate (i.e., pay 0 fees).
Use the `submitpackage` RPC to submit packages directly to the node. Warning: this P2P
feature is limited (unlike the `submitpackage` interface, a child with multiple unconfirmed
parents is not supported) and not yet reliable under adversarial conditions. (#28970)
Mempool Policy Changes
----------------------
- Transactions with version number set to 3 are now treated as standard on all networks (#29496),
subject to opt-in Topologically Restricted Until Confirmation (TRUC) transaction policy as
described in [BIP 431](https://github.com/bitcoin/bips/blob/master/bip-0431.mediawiki). The
policy includes limits on spending unconfirmed outputs (#28948), eviction of a previous descendant
if a more incentive-compatible one is submitted (#29306), and a maximum transaction size of 10,000vB
(#29873). These restrictions simplify the assessment of incentive compatibility of accepting or
replacing TRUC transactions, thus ensuring any replacements are more profitable for the node and
making fee-bumping more reliable.
- Pay To Anchor (P2A) is a new standard witness output type for spending,
a newly recognised output template. This allows for key-less anchor
outputs, with compact spending conditions for additional efficiencies on
top of an equivalent `sh(OP_TRUE)` output, in addition to the txid stability
of the spending transaction.
N.B. propagation of this output spending on the network will be limited
until a sufficient number of nodes on the network adopt this upgrade. (#30352)
- Limited package RBF is now enabled, where the proposed conflicting package would result in
a connected component, aka cluster, of size 2 in the mempool. All clusters being conflicted
against must be of size 2 or lower. (#28984)
- The default value of the `-mempoolfullrbf` configuration option has been changed from 0 to 1,
i.e. `mempoolfullrbf=1`. (#30493)
Updated RPCs
------------
- The `dumptxoutset` RPC now returns the UTXO set dump in a new and
improved format. Correspondingly, the `loadtxoutset` RPC now expects
this new format in the dumps it tries to load. Dumps with the old
format are no longer supported and need to be recreated using the
new format to be usable. (#29612)
- AssumeUTXO mainnet parameters have been added for height 840,000.
This means the `loadtxoutset` RPC can now be used on mainnet with
the matching UTXO set from that height. (#28553)
- The `warnings` field in `getblockchaininfo`, `getmininginfo` and
`getnetworkinfo` now returns all the active node warnings as an array
of strings, instead of a single warning. The current behaviour
can be temporarily restored by running Bitcoin Core with the configuration
option `-deprecatedrpc=warnings`. (#29845)
- Previously when using the `sendrawtransaction` RPC and specifying outputs
that are already in the UTXO set, an RPC error code of `-27` with the
message "Transaction already in block chain" was returned in response.
The error message has been changed to "Transaction outputs already in utxo set"
to more accurately describe the source of the issue. (#30212)
- The default mode for the `estimatesmartfee` RPC has been updated from `conservative` to `economical`,
which is expected to reduce over-estimation for many users, particularly if Replace-by-Fee is an option.
For users that require high confidence in their fee estimates at the cost of potentially over-estimating,
the `conservative` mode remains available. (#30275)
- RPC `scantxoutset` now returns 2 new fields in the "unspents" JSON array: `blockhash` and `confirmations`.
See the scantxoutset help for details. (#30515)
- RPC `submitpackage` now allows 2 new arguments to be passed: `maxfeerate` and `maxburnamount`. See the
subtmitpackage help for details. (#28950)
Changes to wallet-related RPCs can be found in the Wallet section below.
Updated REST APIs
-----------------
- Parameter validation for `/rest/getutxos` has been improved by rejecting
truncated or overly large txids and malformed outpoint indices via raising
an HTTP_BAD_REQUEST "Parse error". These requests were previously handled
silently. (#30482, #30444)
Build System
------------
- GCC 11.1 or later, or Clang 16.0 or later,
are now required to compile Bitcoin Core. (#29091, #30263)
- The minimum required glibc to run Bitcoin Core is now
2.31. This means that RHEL 8 and Ubuntu 18.04 (Bionic)
are no-longer supported. (#29987)
- `--enable-lcov-branch-coverage` has been removed, given
incompatibilities between lcov version 1 & 2. `LCOV_OPTS`
should be used to set any options instead. (#30192)
Updated Settings
----------------
- When running with `-alertnotify`, an alert can now be raised multiple
times instead of just once. Previously, it was only raised when unknown
new consensus rules were activated. Its scope has now been increased to
include all kernel warnings. Specifically, alerts will now also be raised
when an invalid chain with a large amount of work has been detected.
Additional warnings may be added in the future. (#30058)
Changes to GUI or wallet related settings can be found in the GUI or Wallet section below.
Wallet
------
- The wallet now detects when wallet transactions conflict with the mempool. Mempool-conflicting
transactions can be seen in the `"mempoolconflicts"` field of `gettransaction`. The inputs
of mempool-conflicted transactions can now be respent without manually abandoning the
transactions when the parent transaction is dropped from the mempool, which can cause wallet
balances to appear higher. (#27307)
- A new `max_tx_weight` option has been added to the RPCs `fundrawtransaction`, `walletcreatefundedpsbt`, and `send`.
It specifies the maximum transaction weight. If the limit is exceeded during funding, the transaction will not be built.
The default value is 4,000,000 WU. (#29523)
- A new `createwalletdescriptor` RPC allows users to add new automatically generated
descriptors to their wallet. This can be used to upgrade wallets created prior to the
introduction of a new standard descriptor, such as taproot. (#29130)
- A new RPC `gethdkeys` lists all of the BIP32 HD keys in use by all of the descriptors in the wallet.
These keys can be used in conjunction with `createwalletdescriptor` to create and add single key
descriptors to the wallet for a particular key that the wallet already knows. (#29130)
- The `sendall` RPC can now spend unconfirmed change and will include additional fees as necessary
for the resulting transaction to bump the unconfirmed transactions' feerates to the specified feerate. (#28979)
- In RPC `bumpfee`, if a `fee_rate` is specified, the feerate is no longer restricted
to following the wallet's incremental feerate of 5 sat/vb. The feerate must still be
at least the sum of the original fee and the mempool's incremental feerate. (#27969)
GUI Changes
-----------
- The "Migrate Wallet" menu allows users to migrate any legacy wallet in their wallet
directory, regardless of the wallets loaded. (gui#824)
- The "Information" window now displays the maximum mempool size along with the
mempool usage. (gui#825)
Low-level Changes
=================
Tests
-----
- The BIP94 timewarp attack mitigation is now active on the `regtest` network. (#30681)
- A new `-testdatadir` option has been added to `test_bitcoin` to allow specifying the
location of unit test data directories. (#26564)
Blockstorage
------------
- Block files are now XOR'd by default with a key stored in the blocksdir.
Previous releases of Bitcoin Core or previous external software will not be able to read the blocksdir with a non-zero XOR-key.
Refer to the `-blocksxor` help for more details. (#28052)
Chainstate
----------
- The chainstate database flushes that occur when blocks are pruned will no longer
empty the database cache. The cache will remain populated longer, which significantly
reduces the time for initial block download to complete. (#28280)
Dependencies
------------
- The dependency on Boost.Process has been replaced with cpp-subprocess, which is contained in source.
Builders will no longer need Boost.Process to build with external signer support. (#28981)
Credits
=======
Thanks to everyone who directly contributed to this release:
- 0xb10c
- Alfonso Roman Zubeldia
- Andrew Toth
- AngusP
- Anthony Towns
- Antoine Poinsot
- Anton A
- Ava Chow
- Ayush Singh
- Ben Westgate
- Brandon Odiwuor
- brunoerg
- bstin
- Charlie
- Christopher Bergqvist
- Cory Fields
- crazeteam
- Daniela Brozzoni
- David Gumberg
- dergoegge
- Edil Medeiros
- Epic Curious
- Fabian Jahr
- fanquake
- furszy
- glozow
- Greg Sanders
- hanmz
- Hennadii Stepanov
- Hernan Marino
- Hodlinator
- ishaanam
- ismaelsadeeq
- Jadi
- Jon Atack
- josibake
- jrakibi
- kevkevin
- kevkevinpal
- Konstantin Akimov
- laanwj
- Larry Ruane
- Lőrinc
- Luis Schwab
- Luke Dashjr
- MarcoFalke
- marcofleon
- Marnix
- Martin Saposnic
- Martin Zumsande
- Matt Corallo
- Matthew Zipkin
- Matt Whitlock
- Max Edwards
- Michael Dietz
- Murch
- nanlour
- pablomartin4btc
- Peter Todd
- Pieter Wuille
- @RandyMcMillan
- RoboSchmied
- Roman Zeyde
- Ryan Ofsky
- Sebastian Falbesoner
- Sergi Delgado Segura
- Sjors Provoost
- spicyzboss
- StevenMia
- stickies-v
- stratospher
- Suhas Daftuar
- sunerok
- tdb3
- TheCharlatan
- umiumi
- Vasil Dimov
- virtu
- willcl-ark
As well as to everyone that helped with translations on
[Transifex](https://www.transifex.com/bitcoin/bitcoin/).
-

@ 592295cf:413a0db9
2024-10-05 09:32:22
# Week 30th September
Wiki article on the topic. [sPhil] (https://sphil.xyz/)
Religion politics philosophy history are critical.
They are not objective things.
Week of updates for protocol apps, including Gossip, coracle app, nostrmo, nostur and many others.
-------
Kind7
Tags: K, emoji,a,others
Others threads multi people
--------
Show likes as kind 1
This person liked this post.
Or this post has three likes in your timeline.
The likes I don't know in your timeline really interest you.
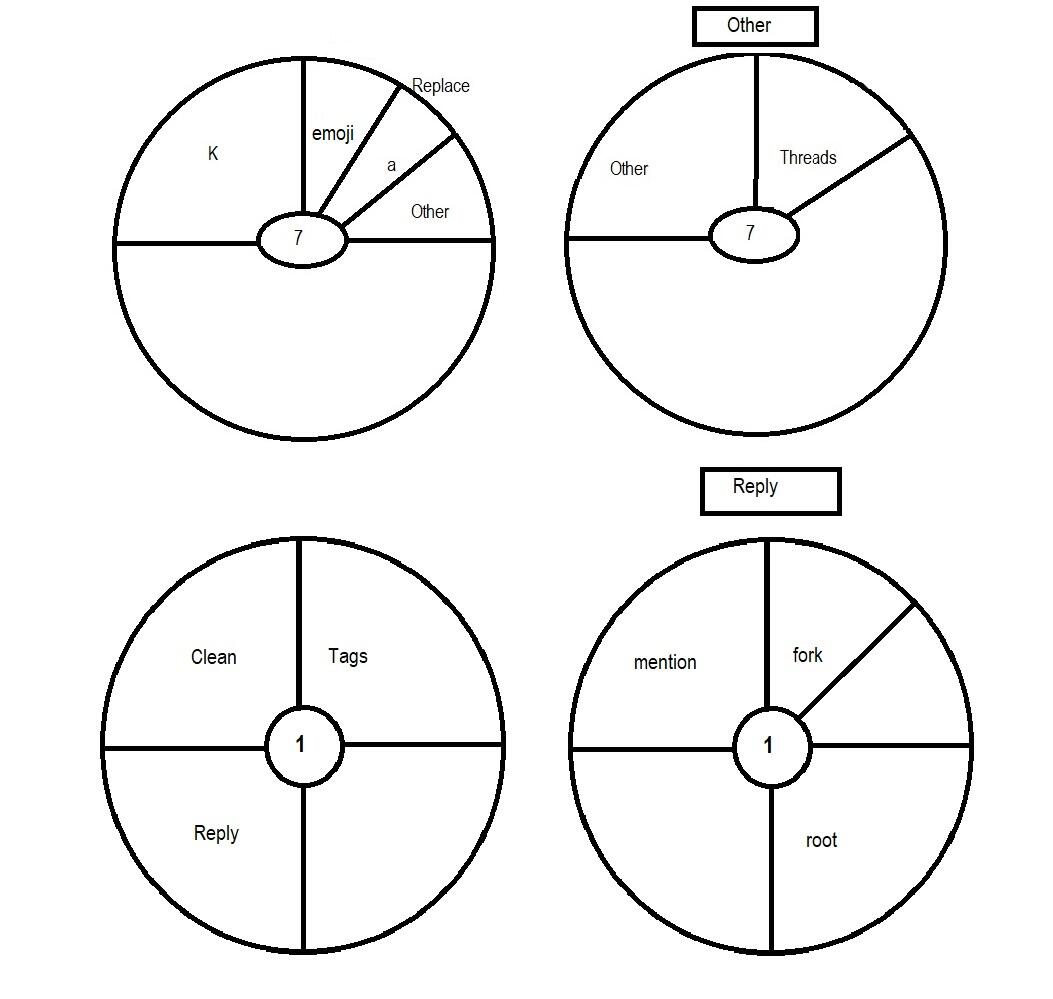
----------
The first book is the bible... Word of Alexandria.
I added cyberspace to the difficult things of the protocol ultra brain things.
Low brain, middle brain, top brain, ultra.
Some alphaama codes
.AA u login
.AA q stuff
.AA q run b
.AA q run f
.AA q close f
high things of alphaama
nostr:nevent1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqlqu2vwpwax7dj420e75yws7g7vyua9e245c0x73c056gunxchluey4q99
-------------------
Comment:
nostr:nevent1qqs8pn0zzhgk5l2raqh736rj3ckm48pfl6r7m72rnz2r2p7lzgmx20gzyqduwzspfzelx9k6x0lrez0j8cl8rtz0lxvqylk8z2ustnfy76jpzqcyqqqqqqgpramhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjsjt5rvu
-----------
You have to get to the point where you have your community relay.
But you have to go down the rabbit hole of relays.
General, search, local, inbox outbox, cache.
Etc until you get to community relay that is being talked about these days because of NIP 29 "Relay-based Groups".
In the end you have to have that table with the various types of relays clearly in your mind.
If the user doesn't think about it, who should think about it, who? if I choose the relays?
-----------
NIP-100 the world to make community for me. NIP-28 + NIP-72.
So you have some structure interoperability with kind1.
But the Channel is another kind.
You arrange the various channels in the community.
No posts need to be approved.
It's useless Protocol users are becoming more reddit users or so. I don't want to deal with these people.
-

@ ec9bd746:df11a9d0
2024-10-04 09:46:21
It's intriguing to me how beer prices have changed since 1999. Today, you can buy Braník on sale for 9.90 Kč, so for 100 Kč you get 10 beers. 25 years ago, you'd get 13.5 beers for the same amount. What does that tell us?
- **The cost of labor and services has gone up a lot**, but people are willing to pay and even expect a certain level of quality. There are way fewer run-down pubs than before.
- **Production has become much more efficient**, so considering inflation and purchasing power, bottled beer is actually cheaper now than it used to be.
In 1995, about 30 years ago, bottled and draft beer cost almost the same—around 7 Kč. ([Source in Czech](https://hn.cz/c1-60157680-jak-se-menily-ceny-co-jste-si-mohli-dovolit-v-roce-1995-a-co-dnes))
**So what's the takeaway?**
1. **A wealthy society can afford much pricier services.**
2. **Prices of basic groceries and fast-moving goods are squeezed to the bone.** The best way to gauge real inflation is at the supermarket, where there's no room for messing with margins, stock levels, seasonality, etc. Everything moves fast, competition is huge, and big retailers are relentless.
Real estate is pricey due to artificial (or bureaucracy-induced) shortages, but meat, milk, beer, bread, etc., are operating on razor-thin profits. That's why they react so quickly—see point 2.
-

@ e6817453:b0ac3c39
2024-09-30 14:52:23
In the modern world of AI, managing vast amounts of data while keeping it relevant and accessible is a significant challenge, mainly when dealing with large language models (LLMs) and vector databases. One approach that has gained prominence in recent years is integrating vector search with metadata, especially in retrieval-augmented generation (RAG) pipelines. Vector search and metadata enable faster and more accurate data retrieval. However, the process of pre- and post-search filtering results plays a crucial role in ensuring data relevance.
<iframe width="560" height="315" src="https://www.youtube.com/embed/BkNqu51et9U?si=lne0jWxdrZPxSgd1" title="YouTube video player" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen></iframe>
## The Vector Search and Metadata Challenge
In a typical vector search, you create embeddings from chunks of text, such as a PDF document. These embeddings allow the system to search for similar items and retrieve them based on relevance. The challenge, however, arises when you need to combine vector search results with structured metadata. For example, you may have timestamped text-based content and want to retrieve the most relevant content within a specific date range. This is where metadata becomes critical in refining search results.
Unfortunately, most vector databases treat metadata as a secondary feature, isolating it from the primary vector search process. As a result, handling queries that combine vectors and metadata can become a challenge, particularly when the search needs to account for a dynamic range of filters, such as dates or other structured data.
## LibSQL and vector search metadata
LibSQL is a more general-purpose SQLite-based database that adds vector capabilities to regular data. Vectors are presented as blob columns of regular tables. It makes vector embeddings and metadata a first-class citizen that naturally builds deep integration of these data points.
```
create table if not exists conversation (
id varchar(36) primary key not null,
startDate real,
endDate real,
summary text,
vectorSummary F32_BLOB(512)
);
```
It solves the challenge of metadata and vector search and eliminates impedance between vector data and regular structured data points in the same storage.
As you can see, you can access vector-like data and start date in the same query.
```
select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance
from conversation
where
${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''}
${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''}
${distance ? `and distance <= ${distance}` : ''}
order by distance
limit ${top};
```
**vector\_distance\_cos** calculated as distance allows us to make a primitive vector search that does a full scan and calculates distances on rows. We could optimize it with CTE and limit search and distance calculations to a much smaller subset of data.
This approach could be calculation intensive and fail on large amounts of data.
Libsql offers a way more effective vector search based on FlashDiskANN vector indexed.
```
vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i
```
**vector\_top\_k** is a table function that searches for the top of the newly created vector search index. As you can see, we could use only vector as a function parameter, and other columns could be used outside of the table function. So, to use a vector index together with different columns, we need to apply some strategies.
Now we get a classical problem of integration vector search results with metadata queries.
## Post-Filtering: A Common Approach
The most widely adopted method in these pipelines is **post-filtering**. In this approach, the system first retrieves data based on vector similarities and then applies metadata filters. For example, imagine you’re conducting a vector search to retrieve conversations relevant to a specific question. Still, you also want to ensure these conversations occurred in the past week.
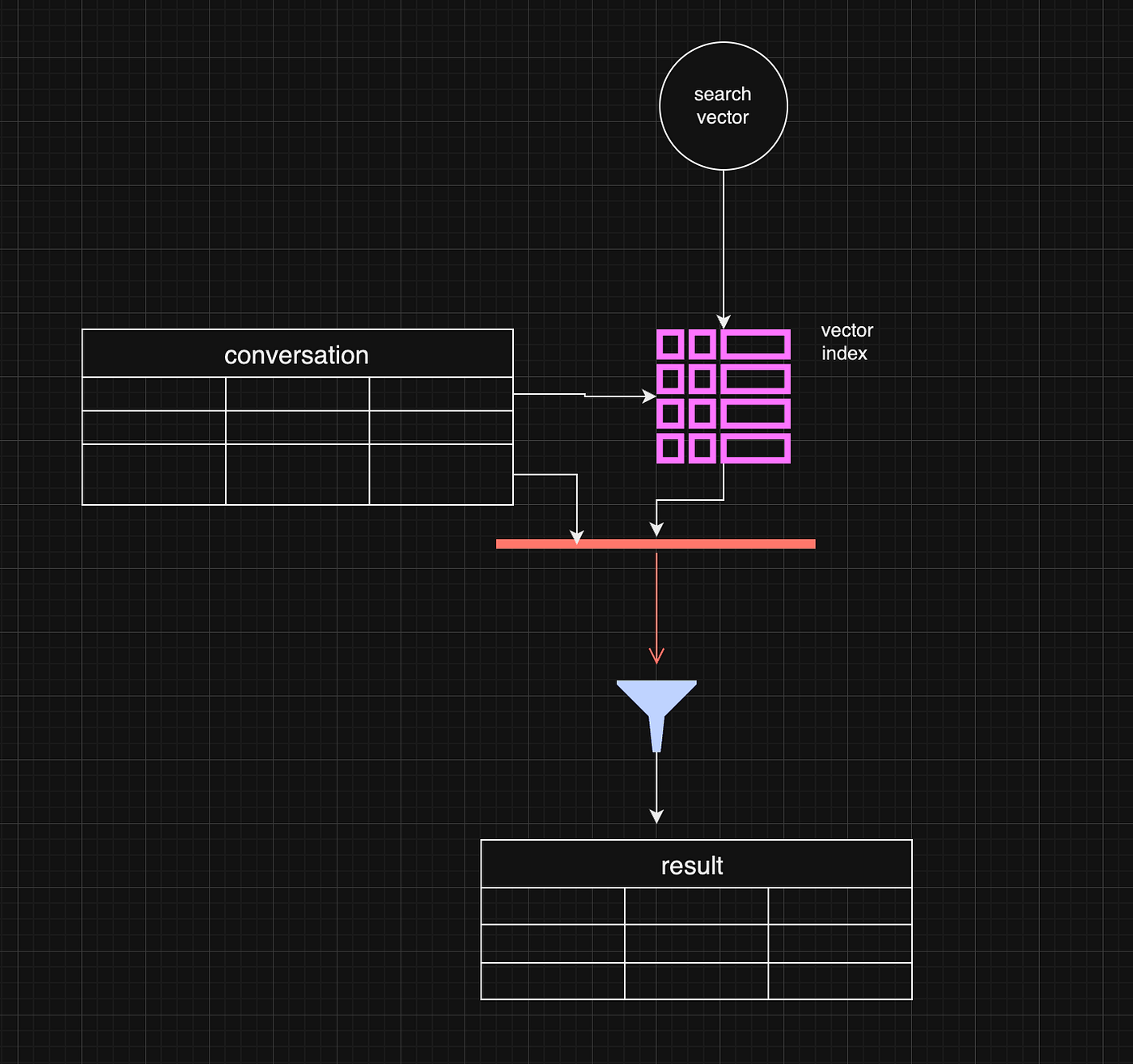
Post-filtering allows the system to retrieve the most relevant vector-based results and subsequently filter out any that don’t meet the metadata criteria, such as date range. This method is efficient when vector similarity is the primary factor driving the search, and metadata is only applied as a secondary filter.
```
const sqlQuery = `
select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance
from vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i
inner join conversation c on i.id = c.rowid
where
${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''}
${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''}
${distance ? `and distance <= ${distance}` : ''}
order by distance
limit ${top};
```
However, there are some limitations. For example, the initial vector search may yield fewer results or omit some relevant data before applying the metadata filter. If the search window is narrow enough, this can lead to complete results.
One working strategy is to make the top value in vector\_top\_K much bigger. Be careful, though, as the function's default max number of results is around 200 rows.
## Pre-Filtering: A More Complex Approach
Pre-filtering is a more intricate approach but can be more effective in some instances. In pre-filtering, metadata is used as the primary filter before vector search takes place. This means that only data that meets the metadata criteria is passed into the vector search process, limiting the scope of the search right from the beginning.
While this approach can significantly reduce the amount of irrelevant data in the final results, it comes with its own challenges. For example, pre-filtering requires a deeper understanding of the data structure and may necessitate denormalizing the data or creating separate pre-filtered tables. This can be resource-intensive and, in some cases, impractical for dynamic metadata like date ranges.
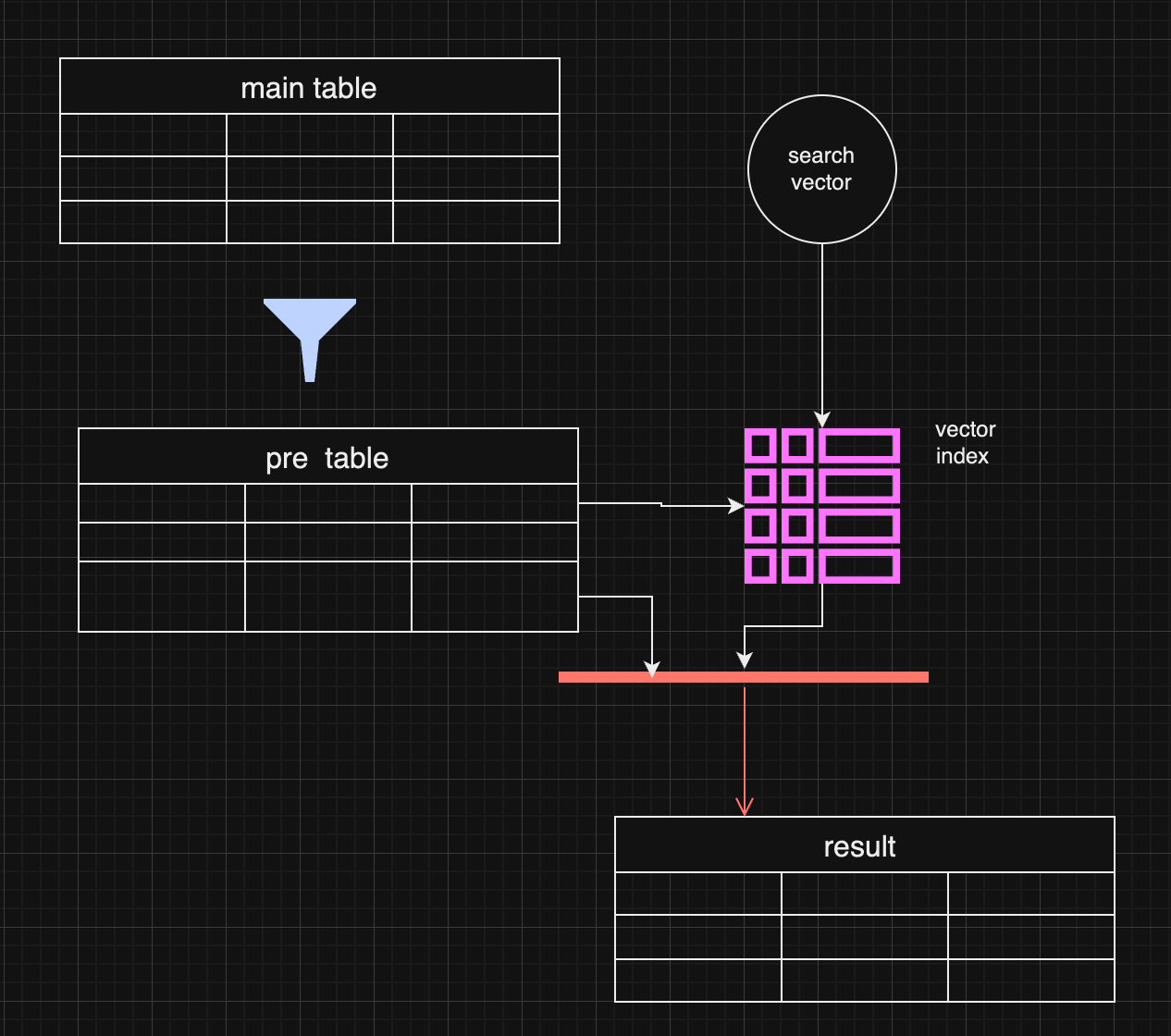
In certain use cases, pre-filtering might outperform post-filtering. For instance, when the metadata (e.g., specific date ranges) is the most important filter, pre-filtering ensures the search is conducted only on the most relevant data.
## Pre-filtering with distance-based filtering
So, we are getting back to an old concept. We do prefiltering instead of using a vector index.
```
WITH FilteredDates AS (
SELECT
c.id,
c.startDate,
c.endDate,
c.summary,
c.vectorSummary
FROM
YourTable c
WHERE
${startDate ? `AND c.startDate >= ${startDate.getTime()}` : ''}
${endDate ? `AND c.endDate <= ${endDate.getTime()}` : ''}
),
DistanceCalculation AS (
SELECT
fd.id,
fd.startDate,
fd.endDate,
fd.summary,
fd.vectorSummary,
vector_distance_cos(fd.vectorSummary, vector(${vector})) AS distance
FROM
FilteredDates fd
)
SELECT
dc.id,
dc.startDate,
dc.endDate,
dc.summary,
dc.distance
FROM
DistanceCalculation dc
WHERE
1=1
${distance ? `AND dc.distance <= ${distance}` : ''}
ORDER BY
dc.distance
LIMIT ${top};
```
It makes sense if the filter produces small data and distance calculation happens on the smaller data set.
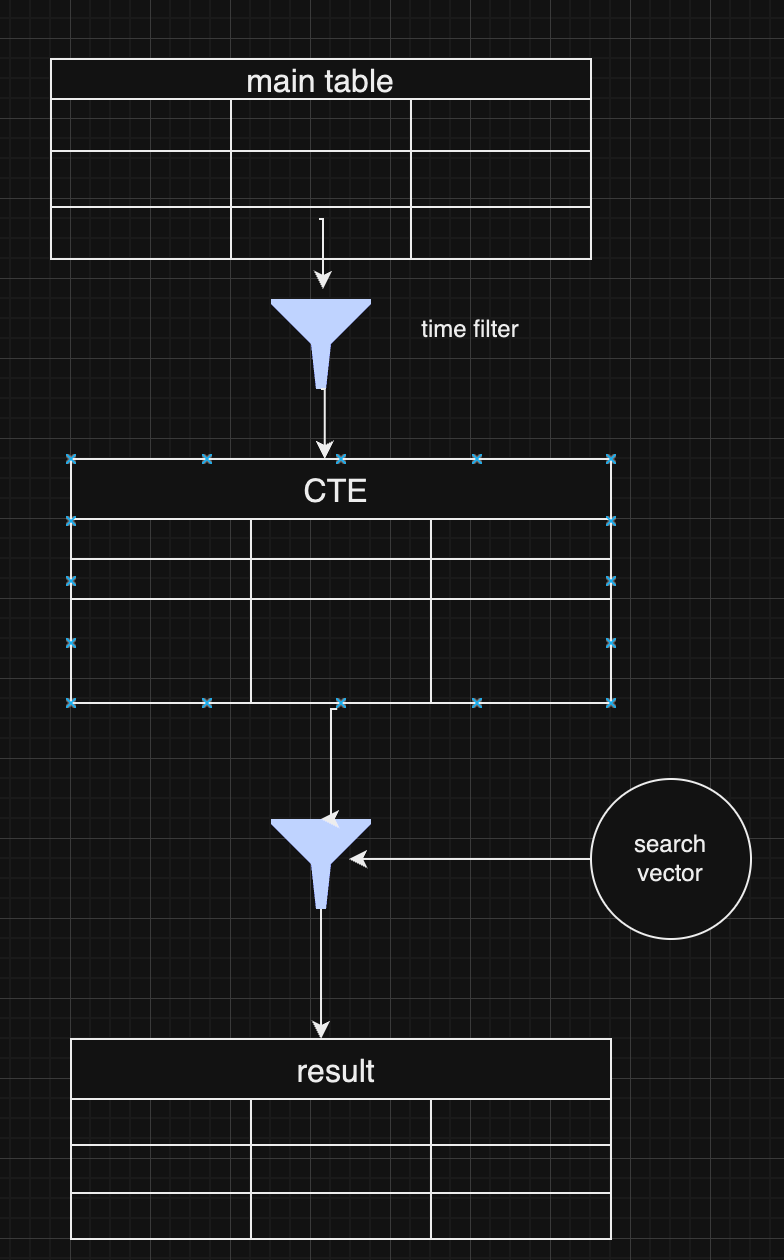
As a pro of this approach, you have full control over the data and get all results without omitting some typical values for extensive index searches.
## Choosing Between Pre and Post-Filtering
Both pre-filtering and post-filtering have their advantages and disadvantages. Post-filtering is more accessible to implement, especially when vector similarity is the primary search factor, but it can lead to incomplete results. Pre-filtering, on the other hand, can yield more accurate results but requires more complex data handling and optimization.
In practice, many systems combine both strategies, depending on the query. For example, they might start with a broad pre-filtering based on metadata (like date ranges) and then apply a more targeted vector search with post-filtering to refine the results further.
## **Conclusion**
Vector search with metadata filtering offers a powerful approach for handling large-scale data retrieval in LLMs and RAG pipelines. Whether you choose pre-filtering or post-filtering—or a combination of both—depends on your application's specific requirements. As vector databases continue to evolve, future innovations that combine these two approaches more seamlessly will help improve data relevance and retrieval efficiency further.
-

@ 472f440f:5669301e
2024-09-25 04:12:35
Last night I had the pleasure of sitting down with Caitlin Long, Founder and CEO of Custodia - a fully reserved bank providing banking services to bitcoin companies, to discuss an affidavit written by Elaine Hetrick of Silvergate Bank. Elaine is the Chief Administrative Officer of Silvergate and wrote an affidavit, a sworn testimony subject to perjury, in which she detailed the events that led to Silvergate voluntarily winding down their business and returning deposits to their customers.
This affidavit is a bombshell because it confirms speculation that Silvergate was solvent in early 2023 and wasn't shut down because of bad risk management on behalf of the bank's management team, but instead was forced to shutter its doors because the Biden Administration, with strong influence from Senator Elizabeth Warren, forced Silvergate's hand because they didn't like that they were banking digital asset companies.
For those who are a bit fuzzy on the details of the narratives that were flying around Silvergate at the time, I'll jog your memory. FTX was a customer of Silvergate's at the time their Ponzi scheme unraveled. As FTX was blowing up, everyone and their mother was scrambling to get their money out of Silvergate because they assumed that since one of the bank's largest counterparties was going bust, the bank must be in trouble too. A sane decision. Especially considering the history of systemically non-important financial institutions this century.
Unless you were paying close attention during this time, you were likely under the impression that Silvergate was a typical fractionally reserved bank that was experiencing a run that led to its inevitable demise. The media made it seem this way. The regulators made it seem this way. And one pompous short seller made it seem this way. However, nothing could be further from the truth.
Here are the most important parts of the affidavit:
>
Silvergate had stabilized, was able to make regulatory capital requirements, and had the capability to continue to serve its customers that had kept their deposits with Silvergate Bank.
Despite this, regulators decided to turn the pressure up and essentially gave Silvergate Bank, and Signature Bank as well, an ultimatum; drastically change your business models immediately by dropping your digital asset customer base or we'll shut you down. There were no hard numbers described in Elaine's testimony, but rumors are that the regulators wanted Silvergate to quickly shrink their exposure to digital asset-related clients to less than 15% of their capital base. At the time, Silvergate's customer base was made up almost entirely of digital asset companies (99.5% to be exact).
The regulators were asking Silvergate to do something that was quite literally impossible given the circumstances. Faced with an impossible task, on March 8th of 2023 Silvergate decided to voluntarily wind down their operations and return deposits back to their customers.
Let's be very clear here, Silvergate did not lose a single penny of customer deposits due to the run on their bank. Management, understanding the volatile nature of the digital asset markets, designed their risk management and capital allocation strategies in a way that would enable them to return dollars to any customer who requested them. And that's exactly what they did when customers came to request their money. They returned EVERY SINGLE PENNY.
This begs the question, "Why did they essentially force Silvergate to shut down?" They seemed to be running a very responsible operation after all. You'd think the regulators would applaud Silvergate's vigilance in risk management on behalf of their customer base. How many banks would have been able to do the same thing if put in the same situation? Probably not many.
The answer to this question is already well known throughout the industry, but Elaine Hetrick's testimony adds some hard evidence that makes it undeniable; Elizabeth Warren, the SEC, the FDIC and the Federal Reserve have been acting in concert to unconstitutionally and extrajudicially target the bitcoin and broader digital asset industry because they do not believe that it should exist. It is a threat to their power structure. The financial system, as it is designed today, gives those who would like to centrally plan the economy and micromanage the lives of American citizens a ton of power. Bitcoin is a threat to that power and they have to do everything in their power to prevent its proliferation.
The targeting of the industry was also confirmed by the aftermath of the NYDFS and FDIC uncharacteristically taking Signature Bank behind the woodshed in the evening of Sunday, March 20th, 2023, despite the fact that Barney Frank and others at the bank were convinced they could handle withdraws come market open the next day.
Signature Bank was ultimately sold to Flagstar Bank. However, they were forced to spin out their digital asset-related accounts before doing so.
This public signaling and sudden regulatory shift made clear that, at least as of the first quarter of 2023, the Federal Bank Regulatory Agencies would not tolerate banks with significant concentrations of digital asset customers, ultimately preventing Silvergate Bank from continuing its digital asset focused business model.
Pretty damning if you ask me. Also, very frustrating and most definitely illegal.
Elizabeth Warren and her gaggle of hall monitors across alphabet soup agencies and the Federal Reserve have been on one massive, unconstitutional, power trip for the last four years. They've besmirched bitcoin and those of us working hard to ensure that the United States of America leads the way forward as bitcoin adoption continues at every turn. Good people striving to make the world a better place.
No one is a better example of this than Alan Lane, the former CEO of Silvergate Bank. I consider Alan a friend and feel supremely confident when I say that he is one of the nicest and thoughtful people I have met in this industry. A man who followed his passion to bring legitimacy and much needed banking services to an industry that the incumbents refused to touch. And he did bring legitimacy. As I explained earlier, Alan and his team understood the volatile nature of the industry and built their firm in a way that took this volatility into account. Silvergate did not fail, they were forced to shut down by Elizabeth Warren and her acolytes at the regulatory agencies.
What's worse, Warren's vendetta against bitcoin and the digital asset industry incited the largest banking crisis this country had seen since 2008. Silvergate and Signature being taken behind the woodshed put everyone on their toes and bank runs started across the country. This led to the failure of First Republic, Silicon Valley Bank and a couple of smaller banks, forced the Fed to step in with their emergency BTFP program, and burdened taxpayers with $40B in FDIC costs that needed to be absorbed as a result. If it weren't for the bailouts things would have gotten completely out of control. All because Elizabeth Warren wants to live in a world in which we are forced to use CBDCs and unable to opt-in to bitcoin.
The euthanasia of Silvergate and Signature are only the tip of the iceberg when it comes to Chokepoint 2.0.
Caitlin Long and Custodia have been in a years long battle with the Federal Reserve to receive a Fed master account so that they can properly serve their customers. For those who are unaware, Custodia is a full-reserve bank that exist to serve bitcoin and digital asset businesses as well as other adjacent businesses like fintechs, banks and funds. Custodia is a chartered bank and special purpose depository institution that has built custody services so that customers can hold bitcoin within their bank accounts alongside their dollar accounts.
Like Silvergate and Signature, Custodia has been singled out and unlawfully denied a master account with the Fed because the Federal Reserve doesn't want a bank like Custodia to exist. Either because they worry about the ramifications of the introduction of a full-reserve bank into a system dominated by fractional-reserve banks or they simply do not want to see bitcoin succeed. If we're being honest, it's probably a combination of the two.
Despite what we, or anyone else, thinks about the potential effect a bank like Custodia could have on the market if it's granted a master account, the Fed's actions are unconstitutional in this case as well. This was made pretty clear (but yet to be determined by a court) in an amicus brief written by Paul Clement on behalf of Custodia earlier this Summer. The Fed is actively undermining the dual-banking system that was set up in this country to enable competition between state chartered banks and the Federal Reserve system.
In the case of Custodia, the Federal Reserve is exhibiting expansive discretionary power that it has never shown before. Custodia is a state chartered special purpose depository institution in the state of Wyoming. Historically, it would be trivial for this type of state chartered bank to get a master account with the Fed. But for whatever reason (we know the reason) the Fed has been denying Custodia their right to this account for a number of years. To the point where Custodia was forced to sue the Federal Reserve and take their case to the courts.
What's interesting about the saga of Custodia and the Fed is that it has forced Custodia's legal team to dig in and highlight where the Fed is overextending its reach and acting arbitrarily. In the amicus brief that was published in July of this year, Paul Clement argues that the way Federal Reserve Bank presidents are chosen is unconstitutional when you take into consideration the fact the these Fed branch presidents are unilaterally undermining state banking laws by denying master accounts.
If they are going to unilaterally undermine state banking laws they need to be appointed by the President or an official acting on behalf of the Executive Branch. Federal Reserve Bank presidents aren't appointed by the President of the United States or any official acting with the authority of the Executive Branch. Instead, they are appointed by their boards, which are controlled by the privately held commercial banks who own them. The Federal Reserve system is clearly acting unconstitutionally when they deny Custodia from being assigned a master account.
The people in power within the federal government and the Federal Reserve system are actively targeting the bitcoin and digital asset industry, acting extrajudicially and making a mockery of the rule of law in the United States. They are completely out of control and it is important that everyone who cares about the future of bitcoin in the United States and the future of the United States more broadly (even if you don't like bitcoin) speaks out and fights against these totalitarians as vehemently as possible. What they are doing is wrong. It's unconstitutional. And it is putting the future of our country at risk.
If the federal government, the regulators and the Federal Reserve do not get out of the way and let law abiding citizens build the businesses they want and associate with businesses they want, those businesses will go elsewhere and the United States will be set back generations as a result.
It's time to put these people in their place and let it be known that freedom will reign supreme in the Land of the Free. Fight!
---
Final thought...
I promised Parker Lewis that I would do cross fit on Friday morning and I'm using today's final thought as an accountability tool.
-

@ c6f7077f:ad5d48fd
2024-09-08 01:24:03
***“The more you learn about something, the more you realize you know nothing.”*** This saying resonates deeply with me. The truth is, **no one really has all the big answers**. Many in the scientific community seem to pretend they do. Let’s explore this further.
#### ***Consider the Most Fundamental Questions***
1. **The Origin of the Universe**
2. **The Origin of Life on Earth**
#### ***The Origin of the Universe***
You might think we have a solid answer: **the Big Bang**. However, this explanation has its limitations, and calling it a “start” can be misleading. In fact, this theory might be entirely wrong. New research challenges the Big Bang theory, and I highly recommend listening to **Sir Roger Penrose** for a deeper understanding.
The only substantial evidence we have is the universe's expansion. Penrose proposes a different hypothesis: **the endless expansion and contraction of the universe**. This idea doesn’t contradict our current understanding.
Thus, the evidence for the Big Bang and Penrose’s theory are both radically different, yet **neither can be definitively proven** over the other. This highlights the **limitations of our current understanding**.
#### ***The Origin of Life on Earth***
The origin of life is even more complex. Life requires three essential components:
- **Proteins** for basic functioning
- **RNA** for storing and replicating genes
- **Lipids** (cell walls) to create separation from the environment
Mathematical models suggest that while proteins and lipids have a reasonable probability of forming, the creation of RNA seems nearly impossible through random mutations in a short time frame. The best explanations indicate that we either lack crucial information or that these RNA molecules—and life as a whole—might have come from **outside sources**. Some scholars even question the entire **random mutation model**.
#### ***The Question of Certainty***
If scientists don’t know the answers, **why do they pretend they do?** In my humble opinion, **It seems they do this to distance science from religion and to close the discussion before the wealthiest can fit God into the narrative,** Interestingly, I’m not alone in believing they closed the books too early.
#### ***Reclaiming Control of Science and Education***
The best way to reclaim control of science and education is to **learn**. If you’re looking for a starting point, I highly recommend:
- **“A Brief History of Time”** by **Stephen Hawking** for physics
- **“Sapiens”** or **“The Selfish Gene”** for evolutionary biology
All three are excellent starting points—densely packed with information and covering a wide range of topics in a concise and accessible manner.
-

@ 460c25e6:ef85065c
2024-08-29 01:07:22
If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
## Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, **they will not receive your updates**.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend:
- 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc.
- 1 personal relay to store a copy of all your content in a place no one can delete. Go to [relay.tools](https://relay.tools/) and never be censored again.
- 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
## Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend:
- 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc.
- 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps.
- 1 really fast relay located in your country: go to [nostr.watch](https://nostr.watch/relays/find) and find relays in your country
Terrible options include:
- nostr.wine should not be here.
- filter.nostr.wine should not be here.
- inbox.nostr.wine should not be here.
## DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. **If you don't have it setup, you will miss DMs**. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are:
- inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you.
- a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details.
- a hidden, but public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
## Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
## Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. **Tagging and searching will not work if there is nothing here.**. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today:
- nostr.wine
- relay.nostr.band
- relay.noswhere.com
## Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
## General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
## My setup
Here's what I use:
1. Go to [relay.tools](https://relay.tools/) and create a relay for yourself.
2. Go to [nostr.wine](https://nostr.wine/) and pay for their subscription.
3. Go to [inbox.nostr.wine](https://inbox.nostr.wine/) and pay for their subscription.
4. Go to [nostr.watch](https://nostr.watch/relays/find) and find a good relay in your country.
5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays:
- nostr.wine
- nos.lol or an in-country relay.
- <your.relay>.nostr1.com
Public Inbox Relays
- nos.lol or an in-country relay
- <your.relay>.nostr1.com
DM Inbox Relays
- inbox.nostr.wine
- <your.relay>.nostr1.com
Private Home Relays
- ws://localhost:4869 (Citrine)
- <your.relay>.nostr1.com (if you want)
Search Relays
- nostr.wine
- relay.nostr.band
- relay.noswhere.com
Local Relays
- ws://localhost:4869 (Citrine)
General Relays
- nos.lol
- relay.damus.io
- relay.primal.net
- nostr.mom
And a few of the recommended relays from Amethyst.
## Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-

@ da18e986:3a0d9851
2024-08-14 13:58:24
After months of development I am excited to officially announce the first version of DVMDash (v0.1). DVMDash is a monitoring and debugging tool for all Data Vending Machine (DVM) activity on Nostr. The website is live at [https://dvmdash.live](https://dvmdash.live) and the code is available on [Github](https://github.com/dtdannen/dvmdash).
Data Vending Machines ([NIP-90](https://github.com/nostr-protocol/nips/blob/master/90.md)) offload computationally expensive tasks from relays and clients in a decentralized, free-market manner. They are especially useful for AI tools, algorithmic processing of user’s feeds, and many other use cases.
The long term goal of DVMDash is to become 1) a place to easily see what’s happening in the DVM ecosystem with metrics and graphs, and 2) provide real-time tools to help developers monitor, debug, and improve their DVMs.
DVMDash aims to enable users to answer these types of questions at a glance:
* What’s the most popular DVM right now?
* How much money is being paid to image generation DVMs?
* Is any DVM down at the moment? When was the last time that DVM completed a task?
* Have any DVMs failed to deliver after accepting payment? Did they refund that payment?
* How long does it take this DVM to respond?
* For task X, what’s the average amount of time it takes for a DVM to complete the task?
* … and more
For developers working with DVMs there is now a visual, graph based tool that shows DVM-chain activity. DVMs have already started calling other DVMs to assist with work. Soon, we will have humans in the loop monitoring DVM activity, or completing tasks themselves. The activity trace of which DVM is being called as part of a sub-task from another DVM will become complicated, especially because these decisions will be made at run-time and are not known ahead of time. Building a tool to help users and developers understand where a DVM is in this activity trace, whether it’s gotten stuck or is just taking a long time, will be invaluable. *For now, the website only shows 1 step of a dvm chain from a user's request.*
One of the main designs for the site is that it is highly _clickable_, meaning whenever you see a DVM, Kind, User, or Event ID, you can click it and open that up in a new page to inspect it.
Another aspect of this website is that it should be fast. If you submit a DVM request, you should see it in DVMDash within seconds, as well as events from DVMs interacting with your request. I have attempted to obtain DVM events from relays as quickly as possible and compute metrics over them within seconds.
This project makes use of a nosql database and graph database, currently set to use mongo db and neo4j, for which there are free, community versions that can be run locally.
Finally, I’m grateful to nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f for supporting this project.
## Features in v0.1:
### Global Network Metrics:
This page shows the following metrics:
- **DVM Requests:** Number of unencrypted DVM requests (kind 5000-5999)
- **DVM Results:** Number of unencrypted DVM results (kind 6000-6999)
- **DVM Request Kinds Seen:** Number of unique kinds in the Kind range 5000-5999 (except for known non-DVM kinds 5666 and 5969)
- **DVM Result Kinds Seen:** Number of unique kinds in the Kind range 6000-6999 (except for known non-DVM kinds 6666 and 6969)
- **DVM Pub Keys Seen:** Number of unique pub keys that have written a kind 6000-6999 (except for known non-DVM kinds) or have published a kind 31990 event that specifies a ‘k’ tag value between 5000-5999
- **DVM Profiles (NIP-89) Seen**: Number of 31990 that have a ‘k’ tag value for kind 5000-5999
- **Most Popular DVM**: The DVM that has produced the most result events (kind 6000-6999)
- **Most Popular Kind**: The Kind in range 5000-5999 that has the most requests by users.
- **24 hr DVM Requests**: Number of kind 5000-5999 events created in the last 24 hrs
- **24 hr DVM Results**: Number of kind 6000-6999 events created in the last 24 hours
- **1 week DVM Requests**: Number of kind 5000-5999 events created in the last week
- **1 week DVM Results**: Number of kind 6000-6999 events created in the last week
- **Unique Users of DVMs**: Number of unique pubkeys of kind 5000-5999 events
- **Total Sats Paid to DVMs**:
- This is an estimate.
- This value is likely a lower bound as it does not take into consideration subscriptions paid to DVMs
- This is calculated by counting the values of all invoices where:
- A DVM published a kind 7000 event requesting payment and containing an invoice
- The DVM later provided a DVM Result for the same job for which it requested payment.
- The assumption is that the invoice was paid, otherwise the DVM would not have done the work
- Note that because there are multiple ways to pay a DVM such as lightning invoices, ecash, and subscriptions, there is no guaranteed way to know whether a DVM has been paid. Additionally, there is no way to know that a DVM completed the job because some DVMs may not publish a final result event and instead send the user a DM or take some other kind of action.
### Recent Requests:
This page shows the most recent 3 events per kind, sorted by created date. You should always be able to find the last 3 events here of all DVM kinds.
### DVM Browser:
This page will either show a profile of a specific DVM, or when no DVM is given in the url, it will show a table of all DVMs with some high level stats. Users can click on a DVM in the table to load the DVM specific page.
### Kind Browser:
This page will either show data on a specific kind including all DVMs that have performed jobs of that kind, or when no kind is given, it will show a table summarizing activity across all Kinds.
### Debug:
This page shows the graph based visualization of all events, users, and DVMs involved in a single job as well as a table of all events in order from oldest to newest. When no event is given, this page shows the 200 most recent events where the user can click on an event in order to debug that job. The graph-based visualization allows the user to zoom in and out and move around the graph, as well as double click on any node in the graph (except invoices) to open up that event, user, or dvm in a new page.
### Playground:
This page is currently under development and may not work at the moment. If it does work, in the current state you can login with NIP-07 extension and broadcast a 5050 event with some text and then the page will show you events from DVMs. This page will be used to interact with DVMs live. A current good alternative to this feature, for some but not all kinds, is [https://vendata.io/](https://vendata.io/).
## Looking to the Future
I originally built DVMDash out of Fear-of-Missing-Out (FOMO); I wanted to make AI systems that were comprised of DVMs but my day job was taking up a lot of my time. I needed to know when someone was performing a new task or launching a new AI or Nostr tool!
I have a long list of DVMs and Agents I hope to build and I needed DVMDash to help me do it; I hope it helps you achieve your goals with Nostr, DVMs, and even AI. To this end, I wish for this tool to be useful to others, so if you would like a feature, please [submit a git issue here](https://github.com/dtdannen/dvmdash/issues/new) or _note_ me on Nostr!
### Immediate Next Steps:
- Refactoring code and removing code that is no longer used
- Improve documentation to run the project locally
- Adding a metric for number of encrypted requests
- Adding a metric for number of encrypted results
### Long Term Goals:
- Add more metrics based on community feedback
- Add plots showing metrics over time
- Add support for showing a multi-dvm chain in the graph based visualizer
- Add a real-time mode where the pages will auto update (currently the user must refresh the page)
- ... Add support for user requested features!
## Acknowledgements
There are some fantastic people working in the DVM space right now. Thank you to nostr:npub1drvpzev3syqt0kjrls50050uzf25gehpz9vgdw08hvex7e0vgfeq0eseet for making python bindings for nostr_sdk and for the recent asyncio upgrades! Thank you to nostr:npub1nxa4tywfz9nqp7z9zp7nr7d4nchhclsf58lcqt5y782rmf2hefjquaa6q8 for answering lots of questions about DVMs and for making the nostrdvm library. Thank you to nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft for making the original DVM NIP and [vendata.io](https://vendata.io/) which I use all the time for testing!
P.S. I rushed to get this out in time for Nostriga 2024; code refactoring will be coming :)
-

@ 30ceb64e:7f08bdf5
2024-08-14 11:51:36
Heres a scenario:
Imagine you have a nostr e-cash/Lightning Wallet and you would like to have a maximum receive balance of 20k split in between 5 mints that enable multipath payments.
Pick 5 mints below to store 4k sats each, the funds are automatically withdrawn to your lightning node at the end of the day.
Stacker News
Robosats
Sparrow
Coinkite
Start9
Rabbit Hole Recap
@siggy47
Damus
LND
Your own mint
originally posted at https://stacker.news/items/648298
-

@ 30ceb64e:7f08bdf5
2024-08-14 11:15:27
>It's wild. I just proved I can build #nostr 'wallet' where I can store the encrypted tokens in a Germany relay and make the lightning payment out of a Singapore mint. All using a #nsec that never leaves my machine.
https://primal.net/e/note15l02rf4r474ck04mlrxxfagyl0z6t04ltsugf9dtph4xxhzfnd4sqpk74n
>I’ve proven to myself that a #nostr wallet can exist across time and space, independently of any one app, server or custodian. The only thing which controls the ‘wallet’ is the generation and control of an #nsec which is free to exist within or flee any jurisdiction.
>In my mind, this lays to rest the notion that a wallet needs to be an app, service, or anything that can be captured commercially or by the state. https://primal.net/e/note13nwsh852x9tfex2jade6vwymhhct8zussxr4zwy7uag24hjc9stq0xsxaf
https://image.nostr.build/07dd1b56d6bb60b13cfe6c19d9384bc3ef198d01af4be9a5c544f791b80b746a.png
>I am thinking about coining the term “nsac” to refer to a wallet-like thing that can exist on #nostr holding your valuable things, such as ecash tokens. I have already implemented a prototype #cashu ecash wallet which looks to be promising.
>So you would have:
#npub - your identity
#nsec - your private key
#nsac - your valuables
>Your #nsac could be the same as your #nsec but better case is to generate as many #nsacs as required.
>Happy to hear feedback!
>For reference, what a ‘sac’ is in the biological sense:
>A **sac** is a biological term referring to a pouch or cavity in an organism that is typically enclosed and may contain fluid, air, or other substances. Sacs can serve various functions depending on their location and role in the body, such as protecting a developing embryo, facilitating the exchange of gases in the lungs, or reducing friction between moving parts in joints
https://primal.net/e/note1snj7y9m6f7lhfzkd2ujzqcvparpgddzmgcgwsgghqvkcyd0rkqhsmmlyla
npub1q6mcr8tlr3l4gus3sfnw6772s7zae6hqncmw5wj27ejud5wcxf7q0nx7d5
Wild stuff freaks, will nostr become the best lightning/E-Cash wallet? Let me know what you think.
originally posted at https://stacker.news/items/648270
-

@ 76c71aae:3e29cafa
2024-08-13 04:30:00
On social media and in the Nostr space in particular, there’s been a lot of debate about the idea of supporting deletion and editing of notes.
Some people think they’re vital features to have, others believe that more honest and healthy social media will come from getting rid of these features. The discussion about these features quickly turns to the feasibility of completely deleting something on a decentralized protocol. We quickly get to the “We can’t really delete anything from the internet, or a decentralized network.” argument. This crowds out how Delete and Edit can mimic elements of offline interactions, how they can be used as social signals.
When it comes to issues of deletion and editing content, what matters more is if the creator can communicate their intentions around their content. Sure, on the internet, with decentralized protocols, there’s no way to be sure something’s deleted. It’s not like taking a piece of paper and burning it. Computers make copies of things all the time, computers don’t like deleting things. In particular, distributed systems tend to use a Kafka architecture with immutable logs, it’s just easier to keep everything around, as deleting and reindexing is hard. Even if the software could be made to delete something, there’s always screenshots, or even pictures of screens. We can’t provably make something disappear.
What we need to do in our software is clearly express intention. A delete is actually a kind of retraction. “I no longer want to associate myself with this content, please stop showing it to people as part of what I’ve published, stop highlighting it, stop sharing it.” Even if a relay or other server keeps a copy, and keeps sharing it, being able to clearly state “hello world, this thing I said, was a mistake, please get rid of it.” Just giving users the chance to say “I deleted this” is a way of showing intention. It’s also a way of signaling that feedback has been heard. Perhaps the post was factually incorrect or perhaps it was mean and the person wants to remove what they said. In an IRL conversation, for either of these scenarios there is some dialogue where the creator of the content is learning something and taking action based on what they’ve learned.
Without delete or edit, there is no option to signal to the rest of the community that you have learned something because of how the content is structured today. On most platforms a reply or response stating one’s learning will be lost often in a deluge of replies on the original post and subsequent posts are often not seen especially when the original goes viral. By providing tools like delete and edit we give people a chance to signal that they have heard the feedback and taken action.
The Nostr Protocol supports delete and expiring notes. It was one of the reasons we switched from secure scuttlebutt to build on Nostr. Our nos.social app offers delete and while we know that not all relays will honor this, we believe it’s important to provide social signaling tools as a means of making the internet more humane.
We believe that the power to learn from each other is more important than the need to police through moral outrage which is how the current platforms and even some Nostr clients work today.
It’s important that we don’t say Nostr doesn’t support delete. Not all apps need to support requesting a delete, some might want to call it a retraction. It is important that users know there is no way to enforce a delete and not all relays may honor their request.
Edit is similar, although not as widely supported as delete. It’s a creator making a clear statement that they’ve created a new version of their content. Maybe it’s a spelling error, or a new version of the content, or maybe they’re changing it altogether. Freedom online means freedom to retract a statement, freedom to update a statement, freedom to edit your own content. By building on these freedoms, we’ll make Nostr a space where people feel empowered and in control of their own media.
-

@ 30ceb64e:7f08bdf5
2024-08-08 16:38:33
SN and Nostr are a match made in heaven. Here are some thoughts on further integration:
## 1. Splash Zapvertising Integration
Both SN and Nostr clients should consider integrating splash zapvertising features, similar to:
- [ZapAdd](https://www.zapadd.com/)
- [Zapper Nostrapps](https://zapper.nostrapps.org/)
These platforms could charge a small fee for coordinating transactions, creating a new revenue stream while promoting content across the Nostr network.
## 2. Transforming SN Territories into Npubs
Stacker News Territories have the potential to become more than just internal communities. By converting them into Npubs (Nostr public keys), we can expand their reach and engagement. A portion of the monthly territory fee could be allocated towards zapvertising the Npub/Territory to the wider Nostr ecosystem.
Here's a visualization of how SN could interact with other Nostr platforms:
https://image.nostr.build/3ba24a8db8bdca6a4cd32fc25139fead4512b783ceb4f94e505eeea21e8167e5.png
## Example: SN Music Territory Npub
Let's consider how an SN Music Territory could function as an Npub:
1. **Automatic Crossposting**: Top daily content is shared to Satlantis, Fountain, and Damus.
2. **Zapvertising**: Promotes engagement, gains followers, and attracts zaps.
3. **Wide Engagement**: Users from Primal, Yakihonne, and Mastodons bridge can like, repost, and zap content.
4. **Referral System Integration**: Works really well with SN's new referral system.
5. **Content Aggregation**: All posts are automatically compiled into an SN Music Territory blog for wider public sharing.
## Benefits and Considerations
While this approach may not immediately make territory ownership profitable, it offers several advantages:
- Enhanced engagement across multiple platforms
- Increased monetization opportunities
- Simplified management for territory owners (no direct Nostr interaction required)
- Expanded reach into the broader Nostr ecosystem
By implementing these ideas, Stacker News can position itself as a central hub within the Nostr universe, facilitating content sharing and engagement across multiple platforms while providing value to both users and territory owners.
It would also be cool to add....
something like shipyard autoposting
something that will allow you to see comments Nostr comments on SN
WOT scores
and an option to use your unified balance nostr wallet.
originally posted at https://stacker.news/items/640607
-

@ f0aca767:dce3306e
2024-08-07 02:47:40
A while back, I posted about The First Descendant and how, despite feeling clunky, and not really having satisfying gun play, it at _least_ seemed to have the ability to satisfy _more_ than Warframe. I _may_ have been wrong about that. I _may_ have sold Warframe a little short in being offered a new, shiny thing that lost its luster pretty damn quickly.
So, let's talk about the shooter-grinder that _maybe_ started it all.
This story goes back all the way to 2014, around a year after Warframe had originally released. I was dating a locksmith at the time. Not very integral to the story, because her being a locksmith has nothing to do with Warframe ... It was just, you know, the biggest thing I remember _about_ her (aside from, a year later, telling me she didn't think I was dating material). But, she was staying at my place, and I remember distinctly waking up in the morning to her, on _my_ PC, playing this weird ... ninja space game. It had almost no features, no story, and really all you did was click a mission, then shoot things, and then pick up some loot. Wash, rinse, _repeat_.
There were no flying ship animations, no rotating solar maps, _nothing._
I got into it for about a week or so before I realized I couldn't really take playing a game that was technically in open beta, or even alpha? I don't remember. So, I dropped it. I would revisit it again and again, shooting things, leveling up, and then losing motivation. Until suddenly, one day, the star map was moving, and you could see the ship you were on flying _to those missions._
Amazing.
But I kept going in and out of it like tossing out pairs of socks. At least until around 2016 when an online friend convinced me to join her, because there was some _ridiculous_ mission we had to do called "the Second Dream."
Let's just say, it _blew me away_. Finally. A character creator? And, a **story? **Albeit, you're some kind of Stranger Things-esque powerful teenager who pilots these metal space ninjas, but it was _something_. Evangelion, maybe.
I spent a week figuring out what all was new, ran around with my new human legs, found an open world _thing_ on Earth ...
Yeah, I left the game again ... until 2018, and the Fortuna update. Needless to say, I was blown away, _again_. And, after getting frustrated that I couldn't just _have_ the cool new guns and my own hoverboard in a reasonable amount of time ... I left.
This basically is the theme behind my relationship with Digital Extremes and Warframe. I'm the rubber-band player. Getting real excited about all the honestly really cool stuff, and revolutionary storytelling, and then having my motivation riddled with bullets and swords when faced with the prospect of having to spend time collecting things and grinding reputation.
The cycle begins again.
It's 2024, and I'm back in Warframe, enticed by some wild new expansion announcement that _apparently_ takes you back to ... [1999](https://www.warframe.com/1999)??? HUH?
So, I'm swallowing the grind pill, and I'm doing it. Knocking every mission out, one by one, and I'm _almost_ to the New War.

But, here are my feelings about Warframe, all these years later.
A space ninja MMO is freaking _awesome_. I have like, 20 different warframes, and some of them I've never even tried. I'm account level 8, almost 9, and I'm working on upgrading my own massive capital ship (called a Railjack). The story is gripping, wild, and probably some of the best writing I've _ever_ seen in a game, and I cannot _wait_ to get through to more recent content.
But, despite swallowing that pill, and despite working through toward what I want, that's the one problem that remains with Warframe. The game absolutely **disrespects** your time as a human being.
The Second War: Hey buddy, you need a Railjack and a Necramech before you can continue the story. Frikken' scrub.
Okay, so I have the Railjack, in which you use to engage in space combat that isn't all that much unlike combat in No Man's Sky. But ... the Necramech? Oh ... Oh, you gotta grind a bunch of materials on the dead moon Deimos before you can build it?
Queue the internal screaming. This is why I've left the game 40 times since 2014. I'm _not_ a fan of grinding. I have a full-time job, I have extracurricular things I like to do with my time. Spending hours upon hours collecting materials, so I can build a mech, so I can engage in yet another form of combat, so I can continue the _masterfully crafted_ storyline ... it seems to me like needless barriers to get to what you _actually_ want.
The GAME.
But, sure, I mean, yeah. They need hooks to keep you playing, because if you blast through the storyline, and you don't have to do anything else, you lose your player base. I just wish grinding didn't feel like I suddenly had a second job. But ... I'M GONNA DO IT. I'm not quitting this time.
For real.
If you wanna help me out, my account name is CMDR_N0va.
My overall feelings on Warframe are that it's probably one of the best games _ever_ made, that kind of annoys the absolute _hell_ out of me ... at times.
-

@ 30ceb64e:7f08bdf5
2024-08-05 20:14:03
I feel sorry for the laggards who would pile into bitcoin at the last moment.
They'll be fleeing into bitcoin through crypto scams, fake L2's, AI social engineering attacks, misinformation from trusted sources and cognitive dissonance. In a rapidly shifting open source environment niched in topics that they hardly understand. And at the bottom of the rabbit hole you have personal responsibility and hard work waiting for you.
I'm assuming uncle jims will do well. They essentially become financial advisors (Recommending Bitcoin products and services, Helping them understand and move up the sovereignty ladder, Holding Keys, Running LSP's, Mints, and Relays).
Its just crazy to imagine that we're entering a world were 20 year olds have a better grasp on how to use money, how money works, and why it works that way.....than most studied economics professionals.
Understanding money is a key piece to human flourishing and survival, many will succumb to being slaves of their own ignorance, doomed to live out the rest of their days as hungry ghosts, pulling knobs and levers of which have no real meaning or consequence.
https://cdn.satellite.earth/40f7fa81b77c2097ee499cd63d47e66b245aedb20d9a782f33622427c5179dab.webp
originally posted at https://stacker.news/items/636597
-

@ 3c984938:2ec11289
2024-07-22 11:43:17
## Bienvenide a Nostr!
**Introduccíon**
Es tu primera vez aqui en Nostr? Bienvenides! Nostr es un acrónimo raro para "Notes and Other Stuff Transmitted by Relays" on un solo objetivo; resistirse a la censura. Una alternativa a las redes sociales tradicionales, comunicaciónes, blogging, streaming, podcasting, y feventualmente el correo electronico (en fase de desarrollo) con características descentralizadas que te capacita, usario. Jamas seras molestado por un anuncio, capturado por una entidad centralizada o algoritmo que te monetiza.
Permítame ser su anfitrión! Soy Onigiri! Yo estoy explorando el mundo de Nostr, un protocolo de comunicacíon decentralizada. Yo escribo sobre las herramientas y los desarolladores increíbles de Nostr que dan vida a esta reino.

## Bienvenides a Nostr Wonderland
Estas a punto de entrar a un otro mundo digtal que te hará explotar tu mente de todas las aplicaciones descentralizadas, clientes, sitios que puedes utilizar. Nunca volverás a ver a las comunicaciones ni a las redes sociales de la mesma manera. Todo gracias al carácter criptográfico de nostr, inpirado por la tecnología "blockchain". Cada usario, cuando crean una cuenta en Nostr, recibe un par de llaves: una privada y una publico. Estos son las llaves de tu propio reino. Lo que escribes, cantes, grabes, lo que creas - todo te pertenece.

### Unos llaves de Oro y Plata
Mi amigo y yo llamamos a esto "identidad mediante cifrado" porque tu identidad es cifrado. Tu puedes compartir tu llave de plata "npub" a otros usarios para conectar y seguir. Utiliza tu llave de oro "nsec" para accedar a tu cuenta y exponerte a muchas aplicaciones. Mantenga la llave a buen recaudo en todo momento. Ya no hay razor para estar enjaulado por los terminos de plataformas sociales nunca más.
Onigirl
```
npub18jvyjwpmm65g8v9azmlvu8knd5m7xlxau08y8vt75n53jtkpz2ys6mqqu3
```
### Todavia No tienes un cliente? Seleccione la mejor opción.
Encuentra la aplicación adecuada para ti! Utilice su clave de oro "nsec" para acceder a estas herramientas maravillosas. También puedes visit a esta pagina a ver a todas las aplicaciones. Antes de pegar tu llave de oro en muchas aplicaciones, considera un "signer" (firmante) para los sitios web 3. Por favor, mire la siguiente imagen para más detalles. Consulte también la leyenda.
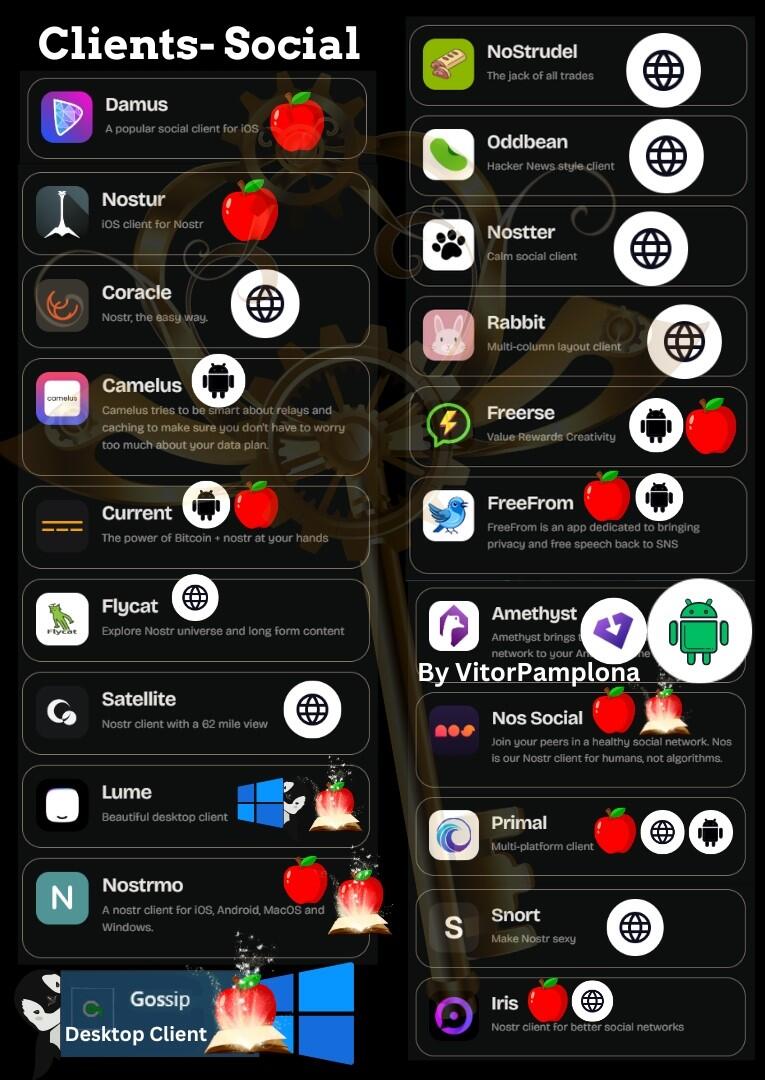
### Get a Signer extension via chrome webstore
Un firmante (o "signer" en inglés) es una extensión del navegador web. Nos2x and NostrConnect son extensiónes ampliamente aceptado para aceder a Nostr. Esto simplifica el proceso de aceder a sitios "web 3". En lugar de copiar y pegar la clave oro "nsec" cada vez, la mantienes guardado en la extensión y le des permiso para aceder a Nostr.

### 👉⚡⚡Obtén una billetera Bitcoin lightning para enviar/recibir Zaps⚡⚡ (Esto es opcional)

Aqui en Nostr, utilizamos la red Lightning de Bitcoin (L2). Nesitaras una cartera lightning para enviar y recibir Satoshis, la denominacion mas chiquita de un Bitcoin. (0.000000001 BTC) Los "zaps" son un tipo de micropago en Nostr. Si te gusta el contenido de un usario, es norma dejarle una propina en la forma de un ¨zap". Por ejemplo, si te gusta este contenido, tu me puedes hacer "zap" con Satoshis para recompensar mi trabajo. Pero apenas llegaste, as que todavia no tienes una cartera. No se preocupe, puedo ayudar en eso!
"[Stacker.News](https://stacker.news/r/Hamstr)" es una plataforma donde los usarios pueden ganar SATS por publicar articulos y interactuar con otros.

Stacker.News es el lugar mas facil para recibir una direccion de cartera Bitcoin Lightning.
1. Acedese con su extensión firmante "signer" - Nos2x or NostrConnect - hace click en tu perfil, un codigo de letras y numeros en la mano superior derecha. Veás algo como esto
2. Haga clic en "edit" y elija un nombre que te guste. Se puede cambiar si deseas en el futuro.

3. Haga clic en "save"
4. Crea una biografía y la comunidad SN son muy acogedora. Te mandarán satoshi para darte la bienvenida.
5. Tu nueva direccion de cartera Bitcoin Lightning aparecerá asi

**^^No le mandas "zaps" a esta direccion; es puramente con fines educativos.**
6. Con tu **Nueva** dirección de monedero Bitcoin Lightning puedes ponerla en cualquier cliente o app de tu elección. Para ello, ve a tu **página de perfil** y bajo la dirección de tu monedero en "**Dirección Lightning**", introduce tu nueva dirección y pulsa **"guardar "** y ya está. Enhorabuena.
👉✨Con el tiempo, es posible que desee pasar a las opciones de auto-custodia y tal vez incluso considerar la posibilidad de auto-alojar su propio nodo LN para una mejor privacidad. La buena noticia es que stacker.news tambien está dejando de ser una cartera custodio.
⭐NIP-05-identidad DNS⭐
Al igual que en Twitter, una marca de verificación es para mostrar que eres del mismo jardín "como un humano", y no un atípico como una mala hierba o, "bot". Pero no de la forma nefasta en que lo hacen las grandes tecnológicas. En el país de las maravillas de Nostr, esto te permite asignar tu llave de plata, "npub", a un identificador DNS. Una vez verificado, puedes gritar para anunciar tu nueva residencia Nostr para compartir.
✨Hay un montón de opciones, pero si has seguido los pasos, esto se vuelve extremadamente fácil.
👉✅¡Haz clic en tu **"Perfil "**, luego en **"Configuración "**, desplázate hasta la parte inferior y pega tu *clave Silver*, **"npub!"** y haz clic en **"Guardar "** y ¡listo! Utiliza tu monedero relámpago de Stacker.news como tu NIP-05. ¡¡¡Enhorabuena!!! ¡Ya estás verificado! Dale unas horas y cuando uses tu cliente **"principal "** deberías ver una marca de verificación.
### Nostr, el infonformista de los servidores.
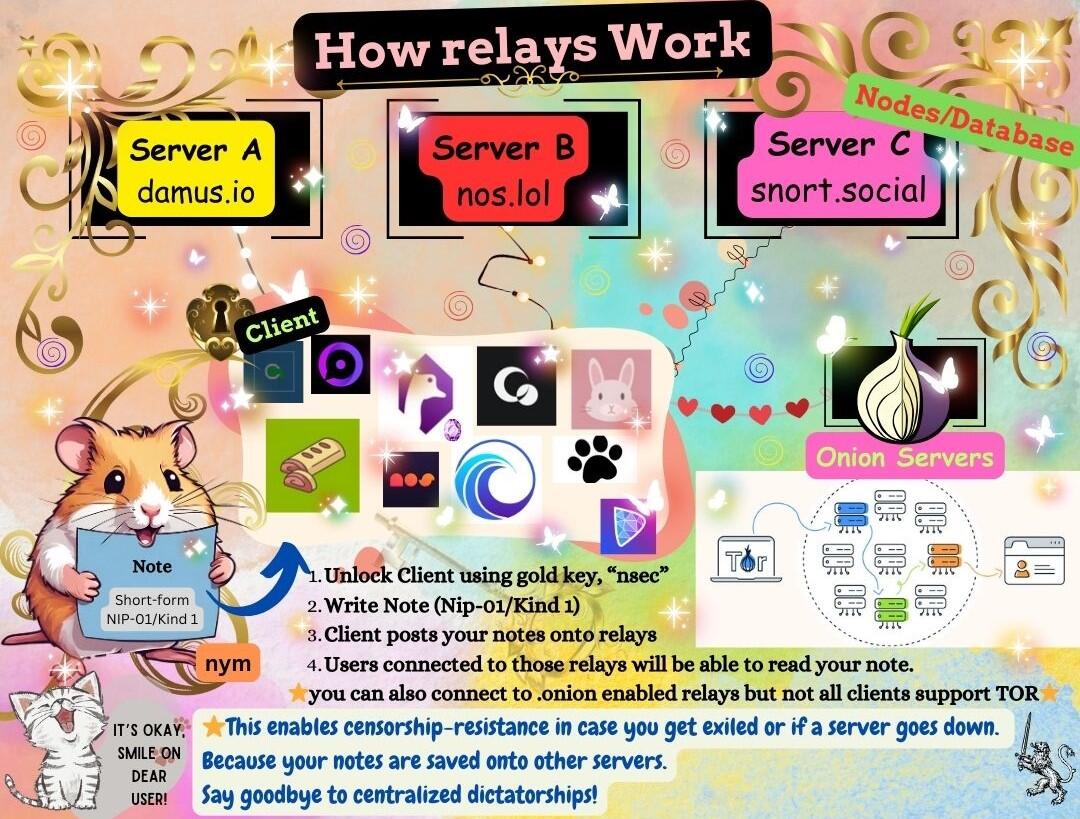
En lugar de utilizar una única instancia o un servidor centralizado, Nostr está construido para que varias bases de datos intercambien mensajes mediante "relés". Los relés, que son neutrales y no discriminatorios, almacenan y difunden mensajes públicos en la red Nostr. Transmiten mensajes a todos los demás clientes conectados a ellos, asegurando las comunicaciones en la red descentralizada.
### ¡Mis amigos en Nostr te dan la bienvenida!
Bienvenida a la fiesta. ¿Le apetece un té?🍵

### ¡Hay mucho mas!
Esto es la punta del iceberg. Síguenme mientras continúo explorando nuevas tierras y a los desarolladores, los caballeres que potencioan este ecosistema. Encuéntrame aquí para mas contenido como este y comparten con otros usarios de nostr. Conozca a los caballeres que luchan por freedomTech (la tecnología de libertad) en Nostr y a los proyectos a los que contribuyen para hacerla realidad.💋
Onigirl
@npub18jvyjwpmm65g8v9azmlvu8knd5m7xlxau08y8vt75n53jtkpz2ys6mqqu3
----
🧡😻Esta guía ha sido cuidadosamente traducida por miggymofongo
Puede seguirla aquí.
@npub1ajt9gp0prf4xrp4j07j9rghlcyukahncs0fw5ywr977jccued9nqrcc0cs
sitio [web](https://miguelalmodo.com/)
-

@ 20986fb8:cdac21b3
2024-07-02 21:08:21
The motivation of building decentralized media protocols is to balance the power of centralized media platforms, and provide an alternative for the public to take part in the curation of information, not just access information. It has to perform checks-and-balances to the centralized media powers, while providing a credible and neutral mechanism for different communities to improve a platform over time. The operation and maintenance of such a media platform should be autonomous, unstoppable, and self-improving.
While a traditional media platform has to align itself with the interests of its owners, shareholders, and donors, the new type of media platform should not be subject to the control of any entity at all times.
The ownership and stewardship of the new media platform should be open and transparent to the public. This is in contrast to state/corporate-controlled media platforms, in which case the public is often not informed of a media platform’s real ownership and stewardship, hence the public cannot be aware of its real purpose, bias, and hidden agendas.
If each individual is more informed, it will be harder to manipulate public opinions, and it will be easier to foster independent judgment within human societies. The positive externality will be enormous. The transition from centralized media platforms to decentralized media platforms speeds up this process.
This article discusses the two pillars to implement a decentralized media technology stack: decentralized publication and decentralized content moderation.
# Decentralization of publication
In a previous article, we extensively discussed the importance of content decentralization. It is the last defense of censorship - content removed or hidden by popular client websites could be stored permanently and be displayed on other (perhaps non-popular) client websites. We also discussed the importance of token economics neutrality, because token economics itself could lead to censorship.
As a non-microblogging platform, [Yakihonne](https://yakihonne.com) is currently one of the most popular clients that implemented [NIP-23](https://github.com/nostr-protocol/nips/blob/master/23.md), attracting bloggers and readers from all over the world to post articles and read contents about Bitcoin and beyond.
> **As of the time of writing of this article, the platform serves users in 116 countries, supporting 18 languages, and has become the most widely used and feature-rich client within the Nostr ecosystem. Yakihonne is also the first Nostr client to support mobile applications and article editing on mobile apps.**

*When publishing articles on Yakihonne.com, you can choose multiple relays to publish the content. Relays can also implement logic to sync articles of their own interests and offer them to clients.*
Joining the relay network is easy. If someone wants to join the relay network, he is able to do so by deploying one of the open source versions of Nostr relays, and starting to store content for the network.
The number of relays serving content within the Nostr protocol is currently quite small. Over the next period of time, it is important to grow the number of reliable relays.
It should be economically viable and encouraging to set up a relay, so that the number of relays can grow over time. Very likely, the number of relays will correspond to the net income of the network, which comes from revenue streams of each of the clients. Therefore, it is foreseeable that the number of reliable relays will be correlated to the traffic of the Nostr protocol in general and therefore, to the traffic of popular clients.
The zap feature (Lightning Zaps) can be used to incentivize relays. But we cannot set unrealistic expectations over zapping. Zapping an article is making a donation. Donation is unpredictable, and it is definitely not a sustainable way to maintain a large, reliable network of relays. One possible solution to this problem is to have profitable clients make continuous contributions to well-performing relays via enforceable protocol setups.

*An ideal incentive mechanism for a relay network is to establish a profit-sharing protocol between clients and the relays.*
# Decentralization of content moderation and content curation
Striking a balance between moderation and anti-moderation has been an almost impossible task for centralized media platforms. Whoever performs the moderation dominates the narratives.
The most recent [community notes](https://communitynotes.twitter.com/guide/en/about/introduction) feature on X took a major step towards community-driven moderation. In community notes, users who are eligible to provide notes can write community notes to a post, and a community can vote for the notes so that the best recognized notes can emerge on the top. It has been proven to be effective in content moderation in many instances, and the ability to add community-backed notes reduced the need for shadow bans.

*Community notes are obviously a more effective system than shadow bans in Jack Dorsey’s Twitter era. At times even Elon Musk himself can be “community noted” is definitely making people trust this system more.*
But it cannot be ignored that users still have to sign up to apply for eligibility for community notes. It is in X's own direction to decide who is eligible and who is not. The voting process of community notes itself could also be subject to censorship, because there is no way to verify the votes.
**This is to say, X has the power to do evil, it doesn’t matter if it does evil or not.**
The countermeasure to balance the power of a centralized media platform is a platform that is not manipulatable by its operating team or share/token holders.
So content moderation has to be permissionless, while verifiability to content moderation mechanisms like community notes.
The first step to developing a decentralized content moderation system is to implement a permissionless community notes system.

*X’s community notes can be censored in two steps: the eligibility review process can filter people based on X’s own preference; the ranking and displaying rules are also controlled by X. In a permissionless community notes system, any relay or even client should be able to implement its own version of community notes, and users can choose their preferred system(s) to work with.*
Notes have to be stored on an open, token economics neutral relay network to ensure their immutability and resistance to censorship. Community members can add notes to any media content, and the notes are distributed to non-related parties who operate the nodes.
## Incentives
The content moderation mechanism needs to be incentivized through the decentralized media protocol.
In a non-sponsored model, income comes from ads or subscription fees, and is distributed to content creators, content relays, and additional network security providers.

In a sponsored model, income is from content sponsors, and further distributed to community note contributors, content relays, and additional network security providers. A sponsored post, in old media platforms, can be quite expensive. The cost to post sponsored content can be dramatically reduced on a decentralized media platform because of the great reduction of content moderation cost.

## Ranking
Community notes can be ranked by either relays or clients. A content relay can rank community notes based on its own preference, and deliver to clients. Clients can also rank community notes based on its rules. Basically, **everyone can rank any post’s community notes.**
In general, community notes ranking algorithms can be stake-based or non-stake based. Stake-based ranking algorithms in general show how people who have a stake in something react to a post. Non-stake based ranking algorithms can be any mechanism, such as reputation-weighted ranks, 1p1v ranks, quadratic voting ranks, random selection, or even asking an AI to rank community notes.
What’s perhaps important is not which ranking algorithm is the best, it’s the flexibility for both the content storage layer and the interfaces (clients) to choose their ideal ranking algorithms. Probably for a client, the best strategy is to provide all ranks from multiple sources, so that people can view community notes from very different angles.
# The Current Status of Bitcoin and the Nostr Protocol
As Nostr is the ideal relay network for decentralized media at this moment, it is necessary to write some notes on the current status of the Bitcoin ecosystem, as Nostr is largely inspired by the Bitcoin network to be decentralized, and is greatly supported by the Bitcoin community.
The Bitcoin community is so far the most legitimate crypto community. It has a very simple mission: to create a decentralized monetary system that is not controlled by centralized powers. The progressive element of the Bitcoin community is relative to the old banking world, where Bitcoin is a completely new and alternative technology stack to the centralized money and finance systems. The conservative element of the Bitcoin community is relative to the other crypto community, where the Bitcoin community is largely skeptical of the motivation and decentralization of them.
In my opinion, the scrutiny Bitcoin community puts upon the rest of the crypto world is totally reasonable. However, as much as Nostr is inspired by the Bitcoin network, it will also go beyond the Bitcoin community, in terms of content.
This is not a bad thing!
If this happens on a big monolithic blockchain, probably the Nostr major contributors will be required to create a token pretty soon and then pay gas fees to the blockchain so that the blockchain’s revenue can increase. The Bitcoin community will never ask that. This gives Nostr enough freedom and flexibility to evolve, while continuously getting support from the Bitcoin community.
However, if Nostr users are forever a subset of Bitcoin users, Nostr will be limited. Nostr is not a subset of Bitcoin, it is not an “ecosystem project” of Bitcoin either (a.k.a., it should not become a “layer-2” of Bitcoin, as some people reason about the future of Bitcoin totally from the analogy of Ethereum).

*In the best world, Nostr and Bitcoin can expand each other’s user base, and create healthy synergy.*
# Conclusion
Yakihonne is, so far, not a protocol. With the products and features it offers, Yakihonne is ready to build up a decentralized media stack. The stack has two pillars : decentralized publication and decentralized content moderation. The former guarantees that content will never be lost; the latter creates a new cost-incentive model to make sure that when content and moderation go permissionless, the platform can still maintain truthfulness and cost-effectiveness. In fact, a decentralized media platform can be more cost-effective than centralized media platforms. So the next step for us is to build this up and experiment with it.
The Flash News and the uncensored notes are introduced for such purpose, and everyone is welcomed to give it a try. Note that it is still in the early stages and various improvements will come eventually, for this your feedback is valuable to us to reach any expectations.
-

@ 6871d8df:4a9396c1
2024-06-12 22:10:51
# Embracing AI: A Case for AI Accelerationism
In an era where artificial intelligence (AI) development is at the forefront of technological innovation, a counter-narrative championed by a group I refer to as the 'AI Decels'—those advocating for the deceleration of AI advancements— seems to be gaining significant traction. After tuning into a recent episode of the [Joe Rogan Podcast](https://fountain.fm/episode/0V35t9YBkOMVM4WRVLYp), I realized that the prevailing narrative around AI was heading in a dangerous direction. Rogan had Aza Raskin and Tristan Harris, technology safety advocates, who released a talk called '[The AI Dilemma](https://www.youtube.com/watch?v=xoVJKj8lcNQ),' on for a discussion. You may know them from the popular documentary '[The Social Dilemma](https://www.thesocialdilemma.com/)' on the dangers of social media. It became increasingly clear that the cautionary stance dominating this discourse might be tipping the scales too far, veering towards an over-regulated future that stifles innovation rather than fostering it.

## Are we moving too fast?
While acknowledging AI's benefits, Aza and Tristan fear it could be dangerous if not guided by ethical standards and safeguards. They believe AI development is moving too quickly and that the right incentives for its growth are not in place. They are concerned about the possibility of "civilizational overwhelm," where advanced AI technology far outpaces 21st-century governance. They fear a scenario where society and its institutions cannot manage or adapt to the rapid changes and challenges introduced by AI.
They argue for regulating and slowing down AI development due to rapid, uncontrolled advancement driven by competition among companies like Google, OpenAI, and Microsoft. They claim this race can lead to unsafe releases of new technologies, with AI systems exhibiting unpredictable, emergent behaviors, posing significant societal risks. For instance, AI can inadvertently learn tasks like sentiment analysis or human emotion understanding, creating potential for misuse in areas like biological weapons or cybersecurity vulnerabilities.
Moreover, AI companies' profit-driven incentives often conflict with the public good, prioritizing market dominance over safety and ethics. This misalignment can lead to technologies that maximize engagement or profits at societal expense, similar to the negative impacts seen with social media. To address these issues, they suggest government regulation to realign AI companies' incentives with safety, ethical considerations, and public welfare. Implementing responsible development frameworks focused on long-term societal impacts is essential for mitigating potential harm.
## This isn't new
Though the premise of their concerns seems reasonable, it's dangerous and an all too common occurrence with the emergence of new technologies. For example, in their example in the podcast, they refer to the technological breakthrough of oil. Oil as energy was a technological marvel and changed the course of human civilization. The embrace of oil — now the cornerstone of industry in our age — revolutionized how societies operated, fueled economies, and connected the world in unprecedented ways. Yet recently, as ideas of its environmental and geopolitical ramifications propagated, the narrative around oil has shifted.
Tristan and Aza detail this shift and claim that though the period was great for humanity, we didn't have another technology to go to once the technological consequences became apparent. The problem with that argument is that we did innovate to a better alternative: nuclear. However, at its technological breakthrough, it was met with severe suspicions, from safety concerns to ethical debates over its use. This overregulation due to these concerns caused a decades-long stagnation in nuclear innovation, where even today, we are still stuck with heavy reliance on coal and oil. The scare tactics and fear-mongering had consequences, and, interestingly, they don't see the parallels with their current deceleration stance on AI.
These examples underscore a critical insight: the initial anxiety surrounding new technologies is a natural response to the unknowns they introduce. Yet, history shows that too much anxiety can stifle the innovation needed to address the problems posed by current technologies. The cycle of discovery, fear, adaptation, and eventual acceptance reveals an essential truth—progress requires not just the courage to innovate but also the resilience to navigate the uncertainties these innovations bring.
Moreover, believing we can predict and plan for all AI-related unknowns reflects overconfidence in our understanding and foresight. History shows that technological progress, marked by unexpected outcomes and discoveries, defies such predictions. The evolution from the printing press to the internet underscores progress's unpredictability. Hence, facing AI's future requires caution, curiosity, and humility. Acknowledging our limitations and embracing continuous learning and adaptation will allow us to harness AI's potential responsibly, illustrating that embracing our uncertainties, rather than pretending to foresee them, is vital to innovation.
The journey of technological advancement is fraught with both promise and trepidation. Historically, each significant leap forward, from the dawn of the industrial age to the digital revolution, has been met with a mix of enthusiasm and apprehension. Aza Raskin and Tristan Harris's thesis in the 'AI Dilemma' embodies the latter.
## Who defines "safe?"
When slowing down technologies for safety or ethical reasons, the issue arises of who gets to define what "safe" or “ethical” mean? This inquiry is not merely technical but deeply ideological, touching the very core of societal values and power dynamics. For example, the push for Diversity, Equity, and Inclusion (DEI) initiatives shows how specific ideological underpinnings can shape definitions of safety and decency.
Take the case of the initial release of Google's AI chatbot, Gemini, which chose the ideology of its creators over truth. Luckily, the answers were so ridiculous that the pushback was sudden and immediate. My worry, however, is if, in correcting this, they become experts in making the ideological capture much more subtle. Large bureaucratic institutions' top-down safety enforcement creates a fertile ground for ideological capture of safety standards.

I claim that the issue is not the technology itself but the lens through which we view and regulate it. Suppose the gatekeepers of 'safety' are aligned with a singular ideology. In that case, AI development would skew to serve specific ends, sidelining diverse perspectives and potentially stifling innovative thought and progress.
In the podcast, Tristan and Aza suggest such manipulation as a solution. They propose using AI for consensus-building and creating "shared realities" to address societal challenges. In practice, this means that when individuals' viewpoints seem to be far apart, we can leverage AI to "bridge the gap." How they bridge the gap and what we would bridge it toward is left to the imagination, but to me, it is clear. Regulators will inevitably influence it from the top down, which, in my opinion, would be the opposite of progress.
In navigating this terrain, we must advocate for a pluralistic approach to defining safety, encompassing various perspectives and values achieved through market forces rather than a governing entity choosing winners. The more players that can play the game, the more wide-ranging perspectives will catalyze innovation to flourish.
## Ownership & Identity
Just because we should accelerate AI forward does not mean I do not have my concerns. When I think about what could be the most devastating for society, I don't believe we have to worry about a Matrix-level dystopia; I worry about freedom. As I explored in "[Whose data is it anyway?](https://cwilbzz.com/whose-data-is-it-anyway/)," my concern gravitates toward the issues of data ownership and the implications of relinquishing control over our digital identities. This relinquishment threatens our privacy and the integrity of the content we generate, leaving it susceptible to the inclinations and profit of a few dominant tech entities.
To counteract these concerns, a paradigm shift towards decentralized models of data ownership is imperative. Such standards would empower individuals with control over their digital footprints, ensuring that we develop AI systems with diverse, honest, and truthful perspectives rather than the massaged, narrow viewpoints of their creators. This shift safeguards individual privacy and promotes an ethical framework for AI development that upholds the principles of fairness and impartiality.
As we stand at the crossroads of technological innovation and ethical consideration, it is crucial to advocate for systems that place data ownership firmly in the hands of users. By doing so, we can ensure that the future of AI remains truthful, non-ideological, and aligned with the broader interests of society.
## But what about the Matrix?
I know I am in the minority on this, but I feel that the concerns of AGI (Artificial General Intelligence) are generally overblown. I am not scared of reaching the point of AGI, and I think the idea that AI will become so intelligent that we will lose control of it is unfounded and silly. Reaching AGI is not reaching consciousness; being worried about it spontaneously gaining consciousness is a misplaced fear. It is a tool created by humans for humans to enhance productivity and achieve specific outcomes.
At a technical level, large language models (LLMs) are trained on extensive datasets and learning patterns from language and data through a technique called "unsupervised learning" (meaning the data is untagged). They predict the next word in sentences, refining their predictions through feedback to improve coherence and relevance. When queried, LLMs generate responses based on learned patterns, simulating an understanding of language to provide contextually appropriate answers. They will only answer based on the datasets that were inputted and scanned.
AI will never be "alive," meaning that AI lacks inherent agency, consciousness, and the characteristics of life, not capable of independent thought or action. AI cannot act independently of human control. Concerns about AI gaining autonomy and posing a threat to humanity are based on a misunderstanding of the nature of AI and the fundamental differences between living beings and machines. AI spontaneously developing a will or consciousness is more similar to thinking a hammer will start walking than us being able to create consciousness through programming. Right now, there is only one way to create consciousness, and I'm skeptical that is ever something we will be able to harness and create as humans. Irrespective of its complexity — and yes, our tools will continue to become evermore complex — machines, specifically AI, cannot transcend their nature as non-living, inanimate objects programmed and controlled by humans.

The advancement of AI should be seen as enhancing human capabilities, not as a path toward creating autonomous entities with their own wills. So, while AI will continue to evolve, improve, and become more powerful, I believe it will remain under human direction and control without the existential threats often sensationalized in discussions about AI's future.
With this framing, we should not view the race toward AGI as something to avoid. This will only make the tools we use more powerful, making us more productive. With all this being said, AGI is still much farther away than many believe.
Today's AI excels in specific, narrow tasks, known as narrow or weak AI. These systems operate within tightly defined parameters, achieving remarkable efficiency and accuracy that can sometimes surpass human performance in those specific tasks. Yet, this is far from the versatile and adaptable functionality that AGI represents.
Moreover, the exponential growth of computational power observed in the past decades does not directly translate to an equivalent acceleration in achieving AGI. AI's impressive feats are often the result of massive data inputs and computing resources tailored to specific tasks. These successes do not inherently bring us closer to understanding or replicating the general problem-solving capabilities of the human mind, which again would only make the tools more potent in _our_ hands.
While AI will undeniably introduce challenges and change the aspects of conflict and power dynamics, these challenges will primarily stem from humans wielding this powerful tool rather than the technology itself. AI is a mirror reflecting our own biases, values, and intentions. The crux of future AI-related issues lies not in the technology's inherent capabilities but in how it is used by those wielding it. This reality is at odds with the idea that we should slow down development as our biggest threat will come from those who are not friendly to us.
## AI Beget's AI
While the unknowns of AI development and its pitfalls indeed stir apprehension, it's essential to recognize the power of market forces and human ingenuity in leveraging AI to address these challenges. History is replete with examples of new technologies raising concerns, only for those very technologies to provide solutions to the problems they initially seemed to exacerbate. It looks silly and unfair to think of fighting a war with a country that never embraced oil and was still primarily getting its energy from burning wood.

The evolution of AI is no exception to this pattern. As we venture into uncharted territories, the potential issues that arise with AI—be it ethical concerns, use by malicious actors, biases in decision-making, or privacy intrusions—are not merely obstacles but opportunities for innovation. It is within the realm of possibility, and indeed, probability, that AI will play a crucial role in solving the problems it creates. The idea that there would be no incentive to address and solve these problems is to underestimate the fundamental drivers of technological progress.
Market forces, fueled by the demand for better, safer, and more efficient solutions, are powerful catalysts for positive change. When a problem is worth fixing, it invariably attracts the attention of innovators, researchers, and entrepreneurs eager to solve it. This dynamic has driven progress throughout history, and AI is poised to benefit from this problem-solving cycle.
Thus, rather than viewing AI's unknowns as sources of fear, we should see them as sparks of opportunity. By tackling the challenges posed by AI, we will harness its full potential to benefit humanity. By fostering an ecosystem that encourages exploration, innovation, and problem-solving, we can ensure that AI serves as a force for good, solving problems as profound as those it might create. This is the optimism we must hold onto—a belief in our collective ability to shape AI into a tool that addresses its own challenges and elevates our capacity to solve some of society's most pressing issues.
## An AI Future
The reality is that it isn't whether AI will lead to unforeseen challenges—it undoubtedly will, as has every major technological leap in history. The real issue is whether we let fear dictate our path and confine us to a standstill or embrace AI's potential to address current and future challenges.
The approach to solving potential AI-related problems with stringent regulations and a slowdown in innovation is akin to cutting off the nose to spite the face. It's a strategy that risks stagnating the U.S. in a global race where other nations will undoubtedly continue their AI advancements. This perspective dangerously ignores that AI, much like the printing press of the past, has the power to democratize information, empower individuals, and dismantle outdated power structures.
The way forward is not less AI but more of it, more innovation, optimism, and curiosity for the remarkable technological breakthroughs that will come. We must recognize that the solution to AI-induced challenges lies not in retreating but in advancing our capabilities to innovate and adapt.
AI represents a frontier of limitless possibilities. If wielded with foresight and responsibility, it's a tool that can help solve some of the most pressing issues we face today. There are certainly challenges ahead, but I trust that with problems come solutions. Let's keep the AI Decels from steering us away from this path with their doomsday predictions. Instead, let's embrace AI with the cautious optimism it deserves, forging a future where technology and humanity advance to heights we can't imagine.
-

@ 3c984938:2ec11289
2024-06-09 14:40:55
I'm having some pain in my heart about the U.S. elections.

Ever since Obama campaigned for office, an increase of young voters have come out of the woodwork. Things have not improved. They've actively told you that "**your vote matters.**" I believe this to be a lie unless any citizen can demand at the gate, at the White House to be allowed to hold and point a gun to the president's head. (**Relax**, this is a hyperbole)
Why so dramatic?
Well, what does the president do? Sign bills, commands the military, nominates new Fed chairman, ambassadors, supreme judges and senior officials all while traveling in luxury planes and living in a white palace for four years.
They promised **Every TIME** to protect citizen rights when they take the oath and office.
*...They've broken this several times, with so-called "emergency-crisis"*

The purpose of a president, today, it seems is to basically hire armed thugs to keep the citizens in check and make sure you "voluntarily continue to be a slave," to the system, hence the IRS. The corruption extends from the cop to the judge and even to politicians. The politicians get paid from lobbyists to create bills in congress for the president to sign. There's no right answer when money is involved with politicians. It is the same if you vote Obama, Biden, Trump, or Haley. They will wield the pen to serve themselves to **say** it will benefit the country.
In the first 100 years of presidency, the government wasn't even a big deal. They didn't even interfere with your life as much as they do today.

^^ You hold the **power** in your hands, don't let them take it. Don't believe me? Try to get a loan from a bank without a signature. Your signature is as good as gold (if not better) and is an original trademark.
Just Don't Vote.
End the Fed.
Opt out.

^^ I choose to form my own path, even if it means leaving everything I knew prior. It doesn't have to be a spiritual thing. Some, have called me religious because of this. We're all capable of greatness and having humanity.
✨Don't have a machine heart with a machine mind. Instead, choose to have a heart like the cowardly lion from the "**Wizard Of Oz.**"
There's no such thing as a good president or politicians.
If there was, they would have issued *non-interest* **Federal Reserve Notes.** Lincoln and Kennedy tried to do this, they got shot.
There's still a banner of America there, but it's so far gone that I cannot even recognize it. However, I only see a bunch of 🏳🌈 pride flags.
✨Patrick Henry got it wrong, when he delivered his speech, "Give me liberty or give me death." Liberty and freedom are two completely different things.
Straightforward from Merriam-Webster
Choose Right or left?
No control, to be 100% without restrictions- free.
✨I disagree with the example sentence given. Because you cannot advocate for human freedom and own slaves, it's contradicting it. Which was common in the founding days.
I can understand many may disagree with me, and you might be thinking, "**This time will be different.**" I, respectfully, disagree, and the proxy wars are proof. Learn the importance of Bitcoin, every **Satoshi** is a step away from corruption.
✨What does it look like to pull the curtains from the "**Wizard of Oz?**"
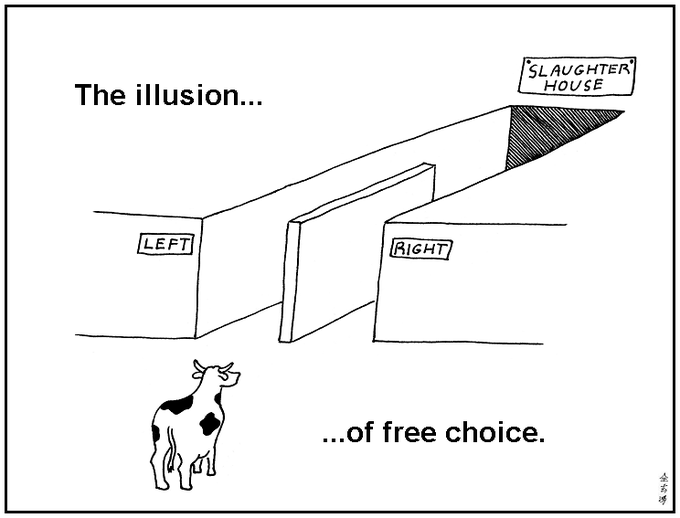
Have you watched the video below, what 30 Trillion dollars in debt looks like visually? Even I was blown away.
https://video.nostr.build/d58c5e1afba6d7a905a39407f5e695a4eb4a88ae692817a36ecfa6ca1b62ea15.mp4

I say this with love. Hear my plea?
Normally, I don't write about anything political. It just feels like a losing game. My energy feels it's in better use to learn new things, write and to create. Even a simple blog post as simple as this. Stack SATs, and stay humble.
<3
Onigirl
-

@ 3bf0c63f:aefa459d
2024-05-21 12:38:08
# Bitcoin transactions explained
A transaction is a piece of data that takes **inputs** and produces **outputs**. Forget about the blockchain thing, Bitcoin is actually just a big tree of transactions. The blockchain is just a way to keep transactions ordered.
Imagine you have 10 satoshis. That means you have them in an unspent transaction output (**UTXO**). You want to spend them, so you create a transaction. The transaction should reference unspent outputs as its inputs. Every transaction has an immutable id, so you use that id plus the index of the output (because transactions can have multiple outputs). Then you specify a **script** that unlocks that transaction and related signatures, then you specify outputs along with a **script** that locks these outputs.

As you can see, there's this lock/unlocking thing and there are inputs and outputs. Inputs must be unlocked by fulfilling the conditions specified by the person who created the transaction they're in. And outputs must be locked so anyone wanting to spend those outputs will need to unlock them.
For most of the cases locking and unlocking means specifying a **public key** whose controller (the person who has the corresponding **private key**) will be able to spend. Other fancy things are possible too, but we can ignore them for now.
Back to the 10 satoshis you want to spend. Since you've successfully referenced 10 satoshis and unlocked them, now you can specify the outputs (this is all done in a single step). You can specify one output of 10 satoshis, two of 5, one of 3 and one of 7, three of 3 and so on. The sum of outputs can't be more than 10. And if the sum of outputs is less than 10 the difference goes to fees. In the first days of Bitcoin you didn't need any fees, but now you do, otherwise your transaction won't be included in any block.

If you're still interested in transactions maybe you could take a look at [this small chapter](https://github.com/bitcoinbook/bitcoinbook/blob/6d1c26e1640ae32b28389d5ae4caf1214c2be7db/ch06_transactions.adoc) of that Andreas Antonopoulos book.
If you hate Andreas Antonopoulos because he is a communist shitcoiner or don't want to read more than half a page, go here: <https://en.bitcoin.it/wiki/Coin_analogy>
-

@ 3c984938:2ec11289
2024-05-09 04:43:15

It's been a journey from the Publishing Forest of Nostr to the open sea of web3. I've come across a beautiful chain of islands and thought. Why not take a break and explore this place? If I'm searching for devs and FOSS, I should search every nook and cranny inside the realm of Nostr. It is quite vast for little old me. I'm just a little hamster and I don't speak in code or binary numbers zeros and ones.

After being in sea for awhile, my heart raced for excitement for what I could find. It seems I wasn't alone, there were others here like me! Let's help spread the message to others about this uncharted realm. See, look at the other sailboats, aren't they pretty? Thanks to some generous donation of SATs, I was able to afford the docking fee.

Ever feel like everyone was going to a party, and you were supposed to dress up, but you missed the memo? Or a comic-con? well, I felt completely underdressed and that's an understatement. Well, turns out there is a some knights around here. Take a peek!

A black cat with a knight passed by very quickly. He was moving too fast for me to track. Where was he going? Then I spotted a group of knights heading in the same direction, so I tagged along. The vibes from these guys was impossible to resist. They were just happy-go-lucky. 🥰They were heading to a tavern on a cliff off the island.

Ehh? a Tavern? Slightly confused, whatever could these knights be doing here? I guess when they're done with their rounds they would here to blow off steam. Things are looking curiouser and curiouser. But the black cat from earlier was here with its rider, whom was dismounting. So you can only guess, where I'm going.

The atmosphere in this pub, was lively and energetic. So many knights spoke among themselves. A group here, another there, but there was one that caught my eye. I went up to a group at a table, whose height towed well above me even when seated. Taking a deep breath, I asked, "Who manages this place?" They unanimous pointed to one waiting for ale at the bar. What was he doing? Watching others talk? How peculiar.

So I went up to him! And introduced myself.
>"Hello I'm Onigirl"
>>"Hello Onigirl, Welcome to Gossip"
>>>"Gossip, what is Gossip?" scratching my head and whiskers.
What is Gossip?
Gossip is FOSS and a great client for **privacy-centric minded nostriches**. It avoids browser tech which by-passes several scripting languages such as JavaScript☕, HTML parsing, rendering, and CSS(Except HTTP GET and Websockets). Using OpenGL-style rendering. **For Nostriches that wish to remain anonymous can use Gossip over TOR.** Mike recommends using QubesOS, Whonix and or Tails. [FYI-Gossip does not natively support tor SOCKS5 proxy]
Most helpful to spill the beans if you're a journalist.

On top of using your nsec or your encryption key, Gossip adds another layer of security over your account with a password login. There's nothing wrong with using the browser extensions (such as nos2x or Flamingo) which makes it super easy to log in to Nostr enable websites, apps, but it does expose you to browser vulnerabilities.
Mike Points out
>"people have already had their private key stolen from other nostr clients,"
so it a concern if you value your account. I most certainly care for mine.

Gossip UI has a simple, and clean interface revolving around NIP-65 also called the “Outbox model." As posted from [GitHub](https://github.com/nostr-protocol/nips/blob/master/65.md),
>"This NIP allows Clients to connect directly with the most up-to-date relay set from each individual user, eliminating the need of broadcasting events to popular relays."
This eliminates clients that track only a specific set of relays which can congest those relays when you publish your note. Also this can be censored, by using Gossip you can publish notes to alternative relays that have not censored you to reach the same followers.
👉The easiest way to translate that is reducing redundancy to publish to popular relays or centralized relays for content reach to your followers.

Cool! What an awesome client, I mean Tavern! What else does this knight do? He reaches for something in his pocket. what is it? A Pocket is a database for storing and retrieving nostr events but mike's written it in Rust with a few extra kinks inspired by Will's nostrdb. Still in development, but it'll be another tool for you dear user! 💖💕💚
Onigirl is proud to present this knights to the community and honor them with kisu. 💋💋💋 Show some 💖💘💓🧡💙💚
👉💋💋Will - jb55 Lord of apples 💋
@npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s
👉💋💋 Mike Knight - Lord of Security 💋
@npub1acg6thl5psv62405rljzkj8spesceyfz2c32udakc2ak0dmvfeyse9p35c

Knights spend a lot of time behind the screen coding for the better of humanity. It is a tough job! Let's appreciate these knights, relay operators, that support this amazing realm of Nostr! FOSS for all!

This article was prompted for the need for privacy and security of your data. They're different, not to be confused.
Recently, Edward Snowden warns Bitcoin devs about the need for privacy, [Quote](https://twitter.com/Snowden/status/1786170805728039127):
>“I've been warning Bitcoin developers for ten years that privacy needs to be provided for at the protocol level. This is the final warning. The clock is ticking.”
Snowden’s comments come after heavy actions of enforcement from Samarai Wallet, Roger Ver, Binance’s CZ, and now the closure of Wasabi Wallet. Additionally, according to [CryptoBriefing](https://cryptobriefing.com/trezor-coinjoin-shutdown/), Trezor is ending it’s CoinJoin integration as well. Many are concerned over the new definition of a money transmitter, which includes even those who don’t touch the funds.
### Help your favorite the hamster

^^Me drowning in notes on your feed. I can only eat so many notes to find you.
👉If there are any XMPP fans on here. I'm open to the idea of opening a public channel, so you could follow me on that as a *forum-like style*. My server of choice would likely be a German server.😀You would be receiving my articles as njump.me style or website-like. GrapeneOS users, you can download Cheogram app from the F-Driod store for free to access. Apple and Andriod users are subjected to pay to download this app, an alternative is **ntalk or conversations**. *If it interests the community, just FYI. Please comment or DM.*
👉If you enjoyed this content, please consider **reposting/sharing** as *my content is easily drowned by notes* on your feed. You could also *join my community under Children_Zone where I post my content.*
An alternative is by following #onigirl Just FYI this feature is currently a little buggy.
Follow as I search for tools and awesome devs to help you dear user live a decentralized life as I explore the realm of Nostr.
Thank you
Fren
-

@ 266815e0:6cd408a5
2024-04-24 23:02:21
> NOTE: this is just a quick technical guide. sorry for the lack of details
## Install NodeJS
Download it from the official website
https://nodejs.org/en/download
Or use nvm
https://github.com/nvm-sh/nvm?tab=readme-ov-file#install--update-script
```bash
wget -qO- https://raw.githubusercontent.com/nvm-sh/nvm/v0.39.7/install.sh | bash
nvm install 20
```
## Clone example config.yml
```bash
wget https://raw.githubusercontent.com/hzrd149/blossom-server/master/config.example.yml -O config.yml
```
## Modify config.yml
```bash
nano config.yml
# or if your that type of person
vim config.yml
```
## Run blossom-server
```bash
npx blossom-server-ts
# or install it locally and run using npm
npm install blossom-server-ts
./node_modules/.bin/blossom-server-ts
```
Now you can open http://localhost:3000 and see your blossom server
And if you set the `dashboard.enabled` option in the `config.yml` you can open http://localhost:3000/admin to see the admin dashboard
-

@ 266815e0:6cd408a5
2024-04-22 22:20:47
While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent
I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS
There were a few things I learned from all these conversations:
1. All the existing solutions have one thing in common. A universal ID of some kind for files
2. HTTP is still good. we don't have to throw the baby out with the bath water
3. nostr could fix this... somehow
Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing...
## An Identity system
An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files
This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends)
## What is blossom?
Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id
## What are Blobs?
blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names
Instead blobs have a sha256 hash (like `b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553`) as an ID
These IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using: `sha256sum bitcoin.pdf` )
## How do the servers work?
Blossom servers expose four endpoints to let clients and users upload and manage blobs
- `GET /<sha256>` (optional file `.ext`)
- `PUT /upload`
- `Authentication`: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#upload-authorization-required)
- Returns a blob descriptor
- `GET /list/<pubkey>`
- Returns an array of blob descriptors
- `Authentication` _(optional)_: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#list-authorization-optional)
- `DELETE /<sha256>`
- `Authentication`: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#delete-authorization-required)
## What is Blossom Drive?
Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs
## What are Drives
Drives are just nostr events (kind `30563`) that store a map of blobs and what filename they should have along with some extra metadata
An example drive event would be
```json
{
"pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5",
"created_at": 1710773987,
"content": "",
"kind": 30563,
"tags": [
[ "name", "Emojis" ],
[ "description", "nostr emojis" ],
[ "d", "emojis" ],
[ "r", "https://cdn.hzrd149.com/" ],
[ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ],
[ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ],
[ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ],
[ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ],
[ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ],
[ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ],
[ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ],
[ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ],
[ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ],
[ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ],
[ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ]
]
}
```
There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at
If your interested, the full event definition is at [github.com/hzrd149/blossom-drive](https://github.com/hzrd149/blossom-drive/blob/master/docs/drive.md)
## Getting started
Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started
### 1. Open the app
Open https://blossom.hzrd149.com
### 2. Login using extension

You can also login using any of the following methods using the input
- NIP-46 with your https://nsec.app or https://flare.pub account
- a NIP-46 connection string
- an `ncryptsec` password protected private key
- a `nsec` unprotected private key (please don't)
- bunker:// URI from nsecbunker
### 3. Add a blossom server

Right now `https://cdn.satellite.earth` is the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript [github.com/hzrd149/blossom-server](https://github.com/hzrd149/blossom-server)
### 4. Start uploading your files
**NOTE: All files upload to blossom drive are public by default. DO NOT upload private files**

### 5. Manage files

## Encrypted drives
There is also the option to encrypt drives using [NIP-49](https://github.com/nostr-protocol/nips/blob/master/49.md) password encryption. although its not tested at all so don't trust it, verify

## Whats next?
I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything
also all the images in this article are stored in one of my blossom drives [here](nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka)
nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
-

@ 362ebffa:492e2719
2024-04-20 15:52:12
Julian Assange (founder of WikiLeaks) released classified documents in 2010, including sensitive U.S. military and diplomatic information. He faced charges of conspiracy and espionage for his role in obtaining and disseminating the documents.
Edward Snowden, (former NSA contractor) leaked classified information in 2013, exposing global surveillance programs. Snowden revealed widespread data collection by intelligence agencies, leading to charges of espionage and theft of government property.
As of today in 2024, both Assange and Snowden are considered whistle blowers by some but face legal consequences for their actions, igniting debates on government transparency and individual rights.
In a sane democratic World, they should be free!
Their efforts to expose government surveillance and misconduct was brave and should be encouraged. But instead they have also faced legal consequences for their actions, with the U.S. government seeking their extradition to face trial on criminal charges.
These cases have sparked debates about government transparency, freedom of the press, national security, and the balance between individual rights and state interests.
Without whistle blowers, government are becoming bullies!
-

@ 3c984938:2ec11289
2024-04-16 17:14:58
## Hello (N)osytrs!

### Yes! I'm calling you an (N)oystr!

Why is that? Because you shine, and I'm not just saying that to get more SATs.
Ordinary Oysters and mussels can produce these beauties! Nothing seriously unique about them, however, with a little time and love each oyster is capable of creating something truly beautiful. I like believing so, at least, given the fact that you're even reading this article; makes you an (N)oystr! This isn't published this on X (formerly known as Twitter), Facebook, Discord, Telegram, or Instagram, which makes you the rare breed! A pearl indeed! I do have access to those platforms, but why create content on a terrible platform knowing I too could be shut down! Unfortunately, many people still use these platforms. This forces individuals to give up their privacy every day. Meta is leading the charge by forcing users to provide a photo ID for verification in order to use their crappy, obsolete site. If that was not bad enough, imagine if you're having a type of disagreement or opinion. Then, Bigtech can easily deplatform you. Umm. So no open debate? Just instantly shut-off users. Whatever, happened to right to a fair trial? Nope, just burning you at the stake as if you're a witch or warlock!
How heinous are the perpetrators and financiers of this? Well, that's opening another can of worms for you.
Imagine your voice being taken away, like the little mermaid. Ariel was lucky to have a prince, but the majority of us? The likelihood that I would be carried away by the current of the sea during a sunset with a prince on a sailboat is zero. And I live on an island, so I'm just missing the prince, sailboat(though I know where I could go to steal one), and red hair. Oh my gosh, now I feel sad.

I do not have the prince, Bob is better!
I do not have mermaid fins, or a shell bra. Use coconut shells, it offers more support!
But, I still have my voice and a killer sunset to die for!
All of that is possible thanks to the work of developers. These knights fight for Freedom Tech by utilizing FOSS, which help provides us with a vibrant ecosystem. Unfortunately, I recently learned that **they are not all *funded***. Knights must eat, drink, and have a work space. This space is where they spend most of their sweat equity on an app or software that may and may not pan out. That brilliance is susceptible to fading, as these individuals are not seen but rather stay behind closed doors. What's worse, if these developers lose faith in their project and decide to join forces with Meta! 😖 Does WhatsApp ring a bell?
Without them, I probably wouldn't be able to create this long form article. Let's cheer them on like cheerleaders.. 👉Unfortunately, there's no cheerleader emoji so you'll just have to settle for a dancing lady, n guy. 💃🕺
Semisol said it beautifully,
npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj
> If we want freedom tech to succeed, the tools that make it possible need to be funded: relays like https://nostr.land, media hosts like https://nostr.build, clients like https://damus.io, etc.
With that thought, Onigirl is pleased to announce the launch of a new series. With a sole focus on free market devs/projects.
# Knights of Nostr!
I'll happily brief you about their exciting project and how it benefits humanity! Let's Support these Magnificent projects, devs, relays, and builders! Our first runner up!
Oppa Fishcake :Lord of Media Hosting
npub137c5pd8gmhhe0njtsgwjgunc5xjr2vmzvglkgqs5sjeh972gqqxqjak37w
Oppa Fishcake with his noble steed!

Think of this as an introduction to learn and further your experience on Nostr! New developments and applications are constantly happening on Nostr. It's enough to make one's head spin. I may also cover FOSS projects(outside of Nostr) as they need some love as well! Plus, you can think of it as another tool to add to your decentralized life. I will not be doing how-to-Nostr guides. I personally feel there are plenty of great guides already available! Which I'm happy to add to curation collection via easily searchable on Yakihonne.
For email updates you can subscribe to my [[https://paragraph.xyz/@onigirl]]
If you like it, send me some 🧡💛💚 hearts💜💗💖 otherwise zap dat⚡⚡🍑🍑peach⚡⚡🍑
~If not me, then at least to our dearest knight!
Thank you from the bottom of my heart for your time and support (N)oystr! Shine bright like a diamond! Share if you care! FOSS power!
Follow on your favorite Nostr Client for the best viewing experience!
[!NOTE]
> I'm using Obsidian + Nostr Writer Plugin; a new way to publish Markdown directly to Nostr.
> I was a little nervous using this because I was used doing them in RStudio; R Markdown.
> Since this is my first article, I sent it to my account as a draft to test it. It's pretty neat.
-

@ c7eda660:efd97c86
2024-04-14 02:02:19
This is a test of Nostr Writer, publishing from Obsidian.
-

@ 47750177:8969e41a
2024-04-08 12:00:00
25.2 Release Notes
==================
Bitcoin Core version 25.2 is now available from:
<https://bitcoincore.org/bin/bitcoin-core-25.2>
This release includes various bug fixes and performance
improvements, as well as updated translations.
Please report bugs using the issue tracker at GitHub:
<https://github.com/bitcoin/bitcoin/issues>
To receive security and update notifications, please subscribe to:
<https://bitcoincore.org/en/list/announcements/join/>
How to Upgrade
==============
If you are running an older version, shut it down. Wait until it has completely
shut down (which might take a few minutes in some cases), then run the
installer (on Windows) or just copy over `/Applications/Bitcoin-Qt` (on macOS)
or `bitcoind`/`bitcoin-qt` (on Linux).
Upgrading directly from a version of Bitcoin Core that has reached its EOL is
possible, but it might take some time if the data directory needs to be migrated. Old
wallet versions of Bitcoin Core are generally supported.
Compatibility
==============
Bitcoin Core is supported and extensively tested on operating systems
using the Linux kernel, macOS 10.15+, and Windows 7 and newer. Bitcoin
Core should also work on most other Unix-like systems but is not as
frequently tested on them. It is not recommended to use Bitcoin Core on
unsupported systems.
Notable changes
===============
### Gui
- gui#774 Fix crash on selecting "Mask values" in transaction view
### RPC
- #29003 rpc: fix getrawtransaction segfault
### Wallet
- #29176 wallet: Fix use-after-free in WalletBatch::EraseRecords
- #29510 wallet: `getrawchangeaddress` and `getnewaddress` failures should not affect keypools for descriptor wallets
### P2P and network changes
- #29412 p2p: Don't process mutated blocks
- #29524 p2p: Don't consider blocks mutated if they don't connect to known prev block
Credits
=======
Thanks to everyone who directly contributed to this release:
- Martin Zumsande
- Sebastian Falbesoner
- MarcoFalke
- UdjinM6
- dergoegge
- Greg Sanders
As well as to everyone that helped with translations on
[Transifex](https://www.transifex.com/bitcoin/bitcoin/).
-

@ 3bf0c63f:aefa459d
2024-03-23 08:57:08
# Nostr is not decentralized nor censorship-resistant
Peter Todd has been [saying this](nostr:nevent1qqsq5zzu9ezhgq6es36jgg94wxsa2xh55p4tfa56yklsvjemsw7vj3cpp4mhxue69uhkummn9ekx7mqpr4mhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet5qy8hwumn8ghj7mn0wd68ytnddaksz9rhwden5te0dehhxarj9ehhsarj9ejx2aspzfmhxue69uhk7enxvd5xz6tw9ec82cspz3mhxue69uhhyetvv9ujuerpd46hxtnfduq3vamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmnyqy28wumn8ghj7un9d3shjtnwdaehgu3wvfnsz9nhwden5te0wfjkccte9ec8y6tdv9kzumn9wspzpn92tr3hexwgt0z7w4qz3fcch4ryshja8jeng453aj4c83646jxvxkyvs4) for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr _today_ is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:

The top one was published to `wss://nostr.wine`, `wss://nos.lol`, `wss://pyramid.fiatjaf.com`. The second was published to the relay where I generally publish all my notes to, `wss://pyramid.fiatjaf.com`, and that is announced on my [NIP-05 file](https://fiatjaf.com/.well-known/nostr.json) and on my [NIP-65](https://nips.nostr.com/65) relay list.
A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are _following me_, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on `wss://pyramid.fiatjaf.com`.
If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is _inherently_ centralized or that it needs a _protocol change_ to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we [drive in the right direction](nostr:naddr1qqykycekxd3nxdpcvgq3zamnwvaz7tmxd9shg6npvchxxmmdqgsrhuxx8l9ex335q7he0f09aej04zpazpl0ne2cgukyawd24mayt8grqsqqqa2803ksy8) we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
---
See also:
- [Censorship-resistant relay discovery in Nostr](nostr:naddr1qqykycekxd3nxdpcvgq3zamnwvaz7tmxd9shg6npvchxxmmdqgsrhuxx8l9ex335q7he0f09aej04zpazpl0ne2cgukyawd24mayt8grqsqqqa2803ksy8)
- [A vision for content discovery and relay usage for basic social-networking in Nostr](nostr:naddr1qqyrxe33xqmxgve3qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cywwjvq)
-

@ 6871d8df:4a9396c1
2024-02-24 22:42:16
In an era where data seems to be as valuable as currency, the prevailing trend in AI starkly contrasts with the concept of personal data ownership. The explosion of AI and the ensuing race have made it easy to overlook where the data is coming from. The current model, dominated by big tech players, involves collecting vast amounts of user data and selling it to AI companies for training LLMs. Reddit recently penned a 60 million dollar deal, Google guards and mines Youtube, and more are going this direction. But is that their data to sell? Yes, it's on their platforms, but without the users to generate it, what would they monetize? To me, this practice raises significant ethical questions, as it assumes that user data is a commodity that companies can exploit at will.
The heart of the issue lies in the ownership of data. Why, in today's digital age, do we not retain ownership of our data? Why can't our data follow us, under our control, to wherever we want to go? These questions echo the broader sentiment that while some in the tech industry — such as the blockchain-first crypto bros — recognize the importance of data ownership, their "blockchain for everything solutions," to me, fall significantly short in execution.
Reddit further complicates this with its current move to IPO, which, on the heels of the large data deal, might reinforce the mistaken belief that user-generated data is a corporate asset. Others, no doubt, will follow suit. This underscores the urgent need for a paradigm shift towards recognizing and respecting user data as personal property.
In my perfect world, the digital landscape would undergo a revolutionary transformation centered around the empowerment and sovereignty of individual data ownership. Platforms like Twitter, Reddit, Yelp, YouTube, and Stack Overflow, integral to our digital lives, would operate on a fundamentally different premise: user-owned data.
In this envisioned future, data ownership would not just be a concept but a practice, with public and private keys ensuring the authenticity and privacy of individual identities. This model would eliminate the private data silos that currently dominate, where companies profit from selling user data without consent. Instead, data would traverse a decentralized protocol akin to the internet, prioritizing user control and transparency.
The cornerstone of this world would be a meritocratic digital ecosystem. Success for companies would hinge on their ability to leverage user-owned data to deliver unparalleled value rather than their capacity to gatekeep and monetize information. If a company breaks my trust, I can move to a competitor, and my data, connections, and followers will come with me. This shift would herald an era where consent, privacy, and utility define the digital experience, ensuring that the benefits of technology are equitably distributed and aligned with the users' interests and rights.
The conversation needs to shift fundamentally. We must challenge this trajectory and advocate for a future where data ownership and privacy are not just ideals but realities. If we continue on our current path without prioritizing individual data rights, the future of digital privacy and autonomy is bleak. Big tech's dominance allows them to treat user data as a commodity, potentially selling and exploiting it without consent. This imbalance has already led to users being cut off from their digital identities and connections when platforms terminate accounts, underscoring the need for a digital ecosystem that empowers user control over data. Without changing direction, we risk a future where our content — and our freedoms by consequence — are controlled by a few powerful entities, threatening our rights and the democratic essence of the digital realm. We must advocate for a shift towards data ownership by individuals to preserve our digital freedoms and democracy.
-

@ 8ce092d8:950c24ad
2024-02-04 23:35:07
# Overview
1. Introduction
2. Model Types
3. Training (Data Collection and Config Settings)
4. Probability Viewing: AI Inspector
5. Match
6. Cheat Sheet
# I. Introduction
AI Arena is the first game that combines human and artificial intelligence collaboration.
AI learns your skills through "imitation learning."
## Official Resources
1. Official Documentation (Must Read): [Everything You Need to Know About AI Arena](https://docs.aiarena.io/everything-you-need-to-know)
Watch the 2-minute video in the documentation to quickly understand the basic flow of the game.
2. Official Play-2-Airdrop competition FAQ Site
https://aiarena.notion.site/aiarena/Gateway-to-the-Arena-52145e990925499d95f2fadb18a24ab0
3. Official Discord (Must Join): https://discord.gg/aiarenaplaytest for the latest announcements or seeking help. The team will also have a exclusive channel there.
4. Official YouTube: https://www.youtube.com/@aiarena because the game has built-in tutorials, you can choose to watch videos.
## What is this game about?
1. Although categorized as a platform fighting game, the core is a probability-based strategy game.
2. Warriors take actions based on probabilities on the AI Inspector dashboard, competing against opponents.
3. The game does not allow direct manual input of probabilities for each area but inputs information through data collection and establishes models by adjusting parameters.
4. Data collection emulates fighting games, but training can be completed using a Dummy As long as you can complete the in-game tutorial, you can master the game controls.
# II. Model Types
Before training, there are three model types to choose from: Simple Model Type, Original Model Type, and Advanced Model Type.
**It is recommended to try the Advanced Model Type after completing at least one complete training with the Simple Model Type and gaining some understanding of the game.**

## Simple Model Type
The Simple Model is akin to completing a form, and the training session is comparable to filling various sections of that form.
This model has 30 buckets. Each bucket can be seen as telling the warrior what action to take in a specific situation. There are 30 buckets, meaning 30 different scenarios. Within the same bucket, the probabilities for direction or action are the same.
For example: What should I do when I'm off-stage — refer to the "Recovery (you off-stage)" bucket.
**For all buckets, refer to this official documentation:**
https://docs.aiarena.io/arenadex/game-mechanics/tabular-model-v2
**Video (no sound): The entire training process for all buckets**
https://youtu.be/1rfRa3WjWEA
Game version 2024.1.10. The method of saving is outdated. Please refer to the game updates.
## Advanced Model Type
The "Original Model Type" and "Advanced Model Type" are based on Machine Learning, which is commonly referred to as combining with AI.
The Original Model Type consists of only one bucket, representing the entire map. If you want the AI to learn different scenarios, you need to choose a "Focus Area" to let the warrior know where to focus. A single bucket means that a slight modification can have a widespread impact on the entire model. This is where the "Advanced Model Type" comes in.
The "Advanced Model Type" can be seen as a combination of the "Original Model Type" and the "Simple Model Type". The Advanced Model Type divides the map into 8 buckets. Each bucket can use many "Focus Area." For a detailed explanation of the 8 buckets and different Focus Areas, please refer to the tutorial page (accessible in the Advanced Model Type, after completing a training session, at the top left of the Advanced Config, click on "Tutorial").

# III. Training (Data Collection and Config Settings)
## Training Process:
1. **Collect Data**
2. **Set Parameters, Train, and Save**
3. **Repeat Step 1 until the Model is Complete**
Training the Simple Model Type is the easiest to start with; refer to the video above for a detailed process.
Training the Advanced Model Type offers more possibilities through the combination of "Focus Area" parameters, providing a higher upper limit. While the Original Model Type has great potential, it's harder to control. Therefore, this section focuses on the "Advanced Model Type."
## 1. What Kind of Data to Collect
1. **High-Quality Data:** Collect purposeful data. Garbage in, garbage out. Only collect the necessary data; don't collect randomly. It's recommended to use Dummy to collect data. However, don't pursue perfection; through parameter adjustments, AI has a certain level of fault tolerance.
2. **Balanced Data:** Balance your dataset. In simple terms, if you complete actions on the left side a certain number of times, also complete a similar number on the right side. While data imbalance can be addressed through parameter adjustments (see below), it's advised not to have this issue during data collection.
3. **Moderate Amount:** A single training will include many individual actions. Collect data for each action 1-10 times. Personally, it's recommended to collect data 2-3 times for a single action. If the effect of a single training is not clear, conduct a second (or even third) training with the same content, but with different parameter settings.
## 2. What to Collect (and Focus Area Selection)
Game actions mimic fighting games, consisting of 4 directions + 6 states (Idle, Jump, Attack, Grab, Special, Shield). Directions can be combined into ↗, ↘, etc. These directions and states can then be combined into different actions.
To make "Focus Area" effective, you need to collect data in training that matches these parameters. For example, for "Distance to Opponent", you need to collect data when close to the opponent and also when far away.
\* Note: While you can split into multiple training sessions, it's most effective to cover different situations within a single training.
Refer to the Simple Config, categorize the actions you want to collect, and based on the game scenario, classify them into two categories: "Movement" and "Combat."
### Movement-Based Actions
#### Action Collection
When the warrior is offstage, regardless of where the opponent is, we require the warrior to return to the stage to prevent self-destruction.
This involves 3 aerial buckets: 5 (Near Blast Zone), 7 (Under Stage), and 8 (Side Of Stage).

\* Note: The background comes from the Tutorial mentioned earlier. The arrows in the image indicate the direction of the action and are for reference only.
\* Note: Action collection should be clean; do not collect actions that involve leaving the stage.
#### Config Settings
In the Simple Config, you can directly choose "Movement" in it.
However, for better customization, it's recommended to use the Advanced Config directly.
- Intensity: The method for setting Intensity will be introduced separately later.
- Buckets: As shown in the image, choose the bucket you are training.
- Focus Area: Position-based parameters:
- Your position (must)
- Raycast Platform Distance, Raycast Platform Type (optional, generally choose these in Bucket 7)
### Combat-Based Actions
**The goal is to direct attacks quickly and effectively towards the opponent, which is the core of game strategy.**
This involves 5 buckets:
- 2 regular situations
- In the air: 6 (Safe Zone)
- On the ground: 4 (Opponent Active)
- 3 special situations on the ground:
- 1 Projectile Active
- 2 Opponent Knockback
- 3 Opponent Stunned
#### 2 Regular Situations

In the in-game tutorial, we learned how to perform horizontal attacks. However, in the actual game, directions expand to 8 dimensions. Imagine having 8 relative positions available for launching hits against the opponent. Our task is to design what action to use for attack or defense at each relative position.
**Focus Area**
- Basic (generally select all)
- Angle to opponent
- Distance to opponent
- Discrete Distance: Choosing this option helps better differentiate between closer and farther distances from the opponent. As shown in the image, red indicates a relatively close distance, and green indicates a relatively distant distance.
- Advanced: Other commonly used parameters
- Direction: different facings to opponent
- Your Elemental Gauge and Discrete Elementals: Considering the special's charge
- Opponent action: The warrior will react based on the opponent's different actions.
- Your action: Your previous action. Choose this if teaching combos.
#### 3 Special Situations on the Ground
Projectile Active, Opponent Stunned, Opponent Knockback
These three buckets can be referenced in the Simple Model Type video. The parameter settings approach is the same as Opponent Active/Safe Zone.
For Projectile Active, in addition to the parameters based on combat, to track the projectile, you also need to select "Raycast Projectile Distance" and "Raycast Projectile On Target."
### 3. Setting "Intensity"
#### Resources
- The "Tutorial" mentioned earlier explains these parameters.
- Official Config Document (2022.12.24):
https://docs.google.com/document/d/1adXwvDHEnrVZ5bUClWQoBQ8ETrSSKgG5q48YrogaFJs/edit
---
#### TL;DR:
**Epochs:**
- Adjust to fewer epochs if learning is insufficient, increase for more learning.
**Batch Size:**
- Set to the minimum (16) if data is precise but unbalanced, or just want it to learn fast
- Increase (e.g., 64) if data is slightly imprecise but balanced.
- If both imprecise and unbalanced, consider retraining.
**Learning Rate:**
- Maximize (0.01) for more learning but a risk of forgetting past knowledge.
- Minimize for more accurate learning with less impact on previous knowledge.
**Lambda:**
- Reduce for prioritizing learning new things.
**Data Cleaning:**
- Enable "Remove Sparsity" unless you want AI to learn idleness.
- For special cases, like teaching the warrior to use special moves when idle, refer to this tutorial video: https://discord.com/channels/1140682688651612291/1140683283626201098/1195467295913431111
**Personal Experience:**
- Initial training with settings: 125 epochs, batch size 16, learning rate 0.01, lambda 0, data cleaning enabled.
- Prioritize Multistream, sometimes use Oversampling.
- Fine-tune subsequent training based on the mentioned theories.
# IV. Probability Viewing: AI Inspector
The dashboard consists of "Direction + Action."
Above the dashboard, you can see the "Next Action" – the action the warrior will take in its current state.
The higher the probability, the more likely the warrior is to perform that action, indicating a quicker reaction.
It's essential to note that when checking the Direction, the one with the highest visual representation may not have the highest numerical value. To determine the actual value, hover the mouse over the graphical representation, as shown below, where the highest direction is "Idle."

In the map, you can drag the warrior to view the probabilities of the warrior in different positions. Right-click on the warrior with the mouse to change the warrior's facing. The status bar below can change the warrior's state on the map.

When training the "Opponent Stunned, Opponent Knockback" bucket, you need to select the status below the opponent's status bar. If you are focusing on "Opponent action" in the Focus Zone, choose the action in the opponent's status bar. If you are focusing on "Your action" in the Focus Zone, choose the action in your own status bar. When training the "Projectile Active" Bucket, drag the projectile on the right side of the dashboard to check the status.
**Next**
The higher the probability, the faster the reaction. However, be cautious when the action probability reaches 100%. This may cause the warrior to be in a special case of "State Transition," resulting in unnecessary "Idle" states.
> Explanation:
> In each state a fighter is in, there are different "possible transitions". For example, from falling state you cannot do low sweep because low sweep requires you to be on the ground. For the shield state, we do not allow you to directly transition to headbutt. So to do headbutt you have to first exit to another state and then do it from there (assuming that state allows you to do headbutt). This is the reason the fighter runs because "run" action is a valid state transition from shield.
[Source](https://discord.com/channels/848599369879388170/1079903287760928819/1160049804844470292)
# V. Learn from Matches
After completing all the training, your model is preliminarily finished—congratulations! The warrior will step onto the arena alone and embark on its debut!
Next, we will learn about the strengths and weaknesses of the warrior from battles to continue refining the warrior's model.
In matches, besides appreciating the performance, pay attention to the following:
1. **Movement, i.e., Off the Stage:** Observe how the warrior gets eliminated. Is it due to issues in the action settings at a certain position, or is it a normal death caused by a high percentage? The former is what we need to avoid and optimize.
2. **Combat:** Analyze both sides' actions carefully. Observe which actions you and the opponent used in different states. Check which of your hits are less effective, and how does the opponent handle different actions, etc.
The approach to battle analysis is similar to the thought process in the "Training", helping to have a more comprehensive understanding of the warrior's performance and making targeted improvements.
# VI. Cheat Sheet
**Training**
1. Click "Collect" to collect actions.
2. "Map - Data Limit" is more user-friendly. Most players perform initial training on the "Arena" map.
3. Switch between the warrior and the dummy: Tab key (keyboard) / Home key (controller).
4. Use "Collect" to make the opponent loop a set of actions.
5. Instantly move the warrior to a specific location: Click "Settings" - SPAWN - Choose the desired location on the map - On. Press the Enter key (keyboard) / Start key (controller) during training.
**Inspector**
1. Right-click on the fighter to change their direction. Drag the fighter and observe the changes in different positions and directions.
2. When satisfied with the training, click "Save."
3. In "Sparring" and "Simulation," use "Current Working Model."
4. If satisfied with a model, then click "compete." The model used in the rankings is the one marked as "competing."
**Sparring / Ranked**
1. Use the Throneroom map only for the top 2 or top 10 rankings.
2. There is a 30-second cooldown between matches. The replays are played for any match. Once the battle begins, you can see the winner on the leaderboard or by right-clicking the page - Inspect - Console. Also, if you encounter any errors or bugs, please send screenshots of the console to the Discord server.
Good luck! See you on the arena!
-

@ 3bf0c63f:aefa459d
2024-01-15 11:15:06
# Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados
- **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente.
- **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados.
- **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua.
- **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer.
- **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos.
- **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas.
- **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade).
- **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis.
- **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade.
- **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho.
- **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho.
- **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma.
- **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças.
- **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família.
- **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente.
- **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo).
- **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas.
- **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente).
- **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica.
- **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar.
- **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico.
- **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais.
- **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil).
- **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória.
- **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles.
- **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas.
- **inflação**: a inflação estimula o endividamento e o consumismo.
- **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas.
- **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo.
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# IPFS problems: Community
I was an avid IPFS user until yesterday. Many many times I asked simple questions for which I couldn't find an answer on the internet in the #ipfs IRC channel on Freenode. Most of the times I didn't get an answer, and even when I got it was rarely by someone who knew IPFS deeply. I've had issues go unanswered on js-ipfs repositories for year – one of these was raising awareness of a problem that then got fixed some months later by a complete rewrite, I closed my own issue after realizing that by myself some couple of months later, I don't think the people responsible for the rewrite were ever acknowledge that he had fixed my issue.
Some days ago I asked some questions about how the IPFS protocol worked internally, sincerely trying to understand the inefficiencies in finding and fetching content over IPFS. I pointed it would be a good idea to have a drawing showing that so people would understand the difficulties (which I didn't) and wouldn't be pissed off by the slowness. I was told to read the whitepaper. I had already the whitepaper, but read again the relevant parts. The whitepaper doesn't explain anything about the DHT and how IPFS finds content. I said that in the room, was told to read again.
Before anyone misread this section, I want to say I understand it's a pain to keep answering people on IRC if you're busy developing stuff of interplanetary importance, and that I'm not paying anyone nor I have the right to be answered. On the other hand, if you're developing a super-important protocol, financed by many millions of dollars and a lot of people are hitting their heads against your software and there's no one to help them; you're always busy but never delivers anything that brings joy to your users, something is very wrong. I sincerely don't know what IPFS developers are working on, I wouldn't doubt they're working on important things if they said that, but what I see – and what many other users see (take a look at the IPFS Discourse forum) is bugs, bugs all over the place, confusing UX, and almost no help.
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# Castas hindus em nova chave
Shudras buscam o máximo bem para os seus próprios corpos; vaishyas o máximo bem para a sua própria vida terrena e a da sua família; kshatriyas o máximo bem para a sociedade e este mundo terreno; brâmanes buscam o máximo bem.
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# Thoughts on Nostr key management
On [Why I don't like NIP-26 as a solution for key management](nostr:naddr1qqyrgceh89nxgdmzqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823ctgmx78) I talked about multiple techniques that could be used to tackle the problem of key management on Nostr.
Here are some ideas that work in tandem:
- [NIP-41](https://github.com/nostr-protocol/nips/blob/master/41.md) (stateless key invalidation)
- [NIP-46](https://github.com/nostr-protocol/nips/blob/master/46.md) (Nostr Connect)
- [NIP-07](https://github.com/nostr-protocol/nips/blob/master/07.md) (signer browser extension)
- [Connected hardware signing devices](https://lnbits.github.io/nostr-signing-device/installer/)
- other things like musig or frostr keys used in conjunction with a semi-trusted server; or other kinds of trusted software, like a dedicated signer on a mobile device that can sign on behalf of other apps; or even a separate protocol that some people decide to use as the source of truth for their keys, and some clients might decide to use that automatically
- there are probably many other ideas
Some premises I have in my mind (that may be flawed) that base my thoughts on these matters (and cause me to not worry too much) are that
- For the vast majority of people, Nostr keys aren't a target as valuable as Bitcoin keys, so they will probably be ok even without any solution;
- Even when you lose everything, identity can be recovered -- slowly and painfully, but still --, unlike money;
- Nostr is not trying to replace all other forms of online communication (even though when I think about this I can't imagine one thing that wouldn't be nice to replace with Nostr) or of offline communication, so there will always be ways.
- For the vast majority of people, losing keys and starting fresh isn't a big deal. It is a big deal when you have followers and an online persona and your life depends on that, but how many people are like that? In the real world I see people deleting social media accounts all the time and creating new ones, people losing their phone numbers or other accounts associated with their phone numbers, and not caring very much -- they just find a way to notify friends and family and move on.
We can probably come up with some specs to ease the "manual" recovery process, like social attestation and explicit signaling -- i.e., Alice, Bob and Carol are friends; Alice loses her key; Bob sends a new Nostr event kind to the network saying what is Alice's new key; depending on how much Carol trusts Bob, she can automatically start following that and remove the old key -- or something like that.
---
One nice thing about some of these proposals, like NIP-41, or the social-recovery method, or the external-source-of-truth-method, is that they don't have to be implemented in any client, they can live in standalone single-purpose microapps that users open or visit only every now and then, and these can then automatically update their follow lists with the latest news from keys that have changed according to multiple methods.
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# IPFS problems: Shitcoinery
IPFS was advertised to the Ethereum community since the beggining as a way to "store" data for their "dApps". I don't think this is harmful in any way, but for some reason it may have led IPFS developers to focus too much on Ethereum stuff. Once I watched a talk showing libp2p developers – despite being ignored by the Ethereum team (that ended up creating their own agnostic p2p library) – dedicating an enourmous amount of work on getting a libp2p app running in the browser talking to a normal Ethereum node.
The always somewhat-abandoned "Awesome IPFS" site is a big repository of "dApps", some of which don't even have their landing page up anymore, useless Ethereum smart contracts that for some reason use IPFS to store whatever the useless data their users produce.
Again, per se it isn't a problem that Ethereum people are using IPFS, but it is at least confusing, maybe misleading, that when you search for IPFS most of the use-cases are actually Ethereum useless-cases.
## See also
* [Bitcoin](nostr:naddr1qqyryveexumnyd3kqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c7nywz4), the only non-shitcoin
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# Economics
Just a bunch of somewhat-related notes.
* [notes on "Economic Action Beyond the Extent of the Market", Per Bylund](nostr:naddr1qqyxxepsx3skgvenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cf5cy3p)
* [Mises' interest rate theory](nostr:naddr1qqyr2dtrxycr2dmrqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c97asm3)
* [Profits, not wages, as the originary factor](nostr:naddr1qqyrge3hxa3rqce4qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c7x67pu)
* [Reisman on opportunity cost](nostr:naddr1qqyrswtr89nxvepkqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cwx7t3v)
* [Money Supply Measurement](nostr:naddr1qqyr2v3cxcunserzqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cya65m9)
* [Per Bylund's insight](nostr:naddr1qqyxvdtzxscxzcenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cuq3unj)
* [Maybe a new approach to the Austrian Business Cycle Theory, some disorganized thoughts](nostr:naddr1qqyrvdecvccxxcejqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cl9wc86)
* [An argument according to which fractional-reserve banking is merely theft and nothing else](nostr:naddr1qqyrywt9v5exydenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cfks90r)
* [Conjecture and criticism](nostr:naddr1qqyrqde5x9snqvfnqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823ce4glh8)
* [Qual é o economista? (piadas)](nostr:naddr1qqyx2vmrx93xgdpjqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c0ckmsx)
* [UBI calculations](nostr:naddr1qqyryenpxe3ryvf4qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cuurj42)
* [Donations on the internet](nostr:naddr1qqyrqwp4xsmnsvtxqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cex8903)
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# tempreites
My first library to get stars on GitHub, was a very stupid templating library that used just HTML and HTML attributes ("DSL-free"). I was inspired by <http://microjs.com/> at the time and ended up not using the library. Probably no one ever did.
- <https://github.com/fiatjaf/tempreites>
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# nix
Pra instalar o [neuron](797984e3.md) fui forçado a baixar e instalar o [nix](https://nixos.org/download.html). Não consegui me lembrar por que não estava usando até hoje aquele maravilhoso sistema de instalar pacotes desde a primeira vez que tentei, anos atrás.
Que sofrimento pra fazer funcionar com o `fish`, mas até que bem menos sofrimento que da outra vez. Tive que instalar um tal de `fish-foreign-environment` (usando o próprio nix!, já que a outra opção era o `oh-my-fish` ou qualquer outra porcaria dessas) e aí usá-lo para aplicar as definições de shell para bash direto no `fish`.
E aí lembrei também que o `/nix/store` fica cheio demais, o negócio instala tudo que existe neste mundo a partir do zero. É só para computadores muito ricos, mas vamos ver como vai ser. Estou gostando do neuron (veja, estou usando como diário), então vou ter que deixar o nix aí.
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# O Bitcoin como um sistema social humano
Afinal de contas, o que é o Bitcoin? Não vou responder a essa pergunta explicando o que é uma "blockchain" ou coisa que o valha, como todos fazem muito pessimamente. [A melhor explicação em português que eu já vi está aqui](nostr:naddr1qqrky6t5vdhkjmspz9mhxue69uhkv6tpw34xze3wvdhk6q3q80cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsxpqqqp65wp3k3fu), mas mesmo assim qualquer explicação jamais será definitiva.
A explicação apenas do protocolo, do que faz um programa `bitcoind` sendo executado em um computador e como ele se comunica com outros em outros computadores, e os incentivos que estão em jogo para garantir com razoável probabilidade que se chegará a um consenso sobre quem é dono de qual parte de qual transação, apesar de não ser complicada demais, exigirá do iniciante que seja compreendida muitas vezes antes que ele se possa se sentir confortável para dizer que entende um pouco.
E essa parte _técnica_, apesar de ter sido o insight fundamental que gerou o evento miraculoso chamado Bitcoin, não é a parte mais importante, hoje. Se fosse, várias dessas outras moedas seriam concorrentes do Bitcoin, mas não são, e jamais poderão ser, porque elas não estão nem próximas de ter os outros elementos que compõem o Bitcoin. São eles:
1. A estrutura
O Bitcoin é um sistema composto de partes independentes.
Existem programadores que trabalham no protocolo e aplicações, e dia após dia novos programadores chegam e outros saem, e eles trabalham às vezes em conjunto, às vezes sem que um se dê conta do outro, às vezes por conta própria, às vezes pagos por empresas interessadas.
Existem os usuários que realizam validação completa, isto é, estão rodando algum programa do Bitcoin e contribuindo para a difusão dos blocos, das transações, rejeitando usuários malignos e evitando ataques de mineradores mal-intencionados.
Existem os poupadores, acumuladores ou os proprietários de bitcoins, que conhecem as possibilidades que o mundo reserva para o Bitcoin, esperam o dia em que o padrão-Bitcoin será uma realidade mundial e por isso mesmo atributem aos seus bitcoins valores muito mais altos do que os preços atuais de mercado, agarrando-se a eles.
Especuladores de "criptomoedas" não fazem parte desse sistema, nem tampouco empresas que [aceitam pagamento](https://bitpay.com/) em bitcoins para imediatamente venderem tudo em troca de dinheiro estatal, e menos ainda [gente que usa bitcoins](https://www.investimentobitcoin.com/) e [a própria marca Bitcoin](https://www.xdex.com.br/) para aplicar seus golpes e coisas parecidas.
2. A cultura
Mencionei que há empresas que pagam programadores para trabalharem no código aberto do BitcoinCore ou de outros programas relacionados à rede Bitcoin -- ou mesmo em aplicações não necessariamente ligadas à camada fundamental do protocolo. Nenhuma dessas empresas interessadas, porém, controla o Bitcoin, e isso é o elemento principal da cultura do Bitcoin.
O propósito do Bitcoin sempre foi ser uma rede aberta, sem chefes, sem política envolvida, sem necessidade de pedir autorização para participar. O fato do próprio Satoshi Nakamoto ter voluntariamente desaparecido das discussões foi fundamental para que o Bitcoin não fosse visto como um sistema dependente dele ou que ele fosse entendido como o chefe. Em outras "criptomoedas" nada disso aconteceu. O chefe supremo do Ethereum continua por aí mandando e desmandando e inventando novos elementos para o protocolo que são automaticamente aceitos por toda a comunidade, o mesmo vale para o Zcash, EOS, Ripple, Litecoin e até mesmo para o Bitcoin Cash. Pior ainda: Satoshi Nakamoto saiu sem nenhum dinheiro, nunca mexeu nos milhares de bitcoins que ele gerou nos primeiros blocos -- enquanto os líderes dessas porcarias supramencionadas cobraram uma fortuna pelo direito de uso dos seus primeiros usuários ou estão aí a até hoje receber dividendos.
Tudo isso e mais outras coisas -- a mentalidade anti-estatal e entusiasta de sistemas p2p abertos dos membros mais proeminentes da comunidade, por exemplo -- faz com que um ar de liberdade e suspeito de tentativas de centralização da moeda sejam percebidos e execrados.
3. A história
A noção de que o Bitcoin não pode ser controlado por ninguém passou em 2017 por [dois testes](https://www.forbes.com/sites/ktorpey/2019/04/23/this-key-part-of-bitcoins-history-is-what-separates-it-from-competitors/#49869b41ae5e) e saiu deles muito reforçada: o primeiro foi a divisão entre Bitcoin (BTC) e Bitcoin Cash (BCH), uma obra de engenharia social que teve um sucesso mediano em roubar parte da marca e dos usuários do verdadeiro Bitcoin e depois a tentativa de tomada por completo do Bitcoin promovida por mais ou menos as mesmas partes interessadas chamada SegWit2x, que fracassou por completo, mas não sem antes atrapalhar e difundir mentiras para todos os lados. Esses dois fracassos provaram que o Bitcoin, mesmo sendo uma comunidade desorganizada, sem líderes claros, está imune à [captura por grupos interessados](https://en.wikipedia.org/wiki/Regulatory_capture), o que é mais um milagre -- ou, como dizem, um [ponto de Schelling](https://en.wikipedia.org/wiki/Focal_point_(game_theory)).
Esse período crucial na história do Bitcoin fez com ficasse claro que _hard-forks_ são essencialmente incompatíveis com a natureza do protocolo, de modo que no futuro não haverá a possibilidade de uma sugestão como a de imprimir mais bitcoins do que o que estava programado sejam levadas a sério (mas, claro, sempre há a possibilidade da cultura toda se perder, as pessoas esquecerem a história e o Bitcoin ser cooptado, eis a importância da auto-educação e da difusão desses princípios).
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# O caso da Grêmio TV
enquanto vinha se conduzindo pela plataforma superior daquela arena que se pensava totalmente preenchida por adeptos da famosa equipe do Grêmio de Porto Alegre, viu-se, como por obra de algum nigromante - dos muitos que existem e estão a todo momento a fazer más obras e a colocar-se no caminhos dos que procuram, se não fazer o bem acima de todas as coisas, a pelo menos não fazer o mal no curso da realização dos seus interesses -, o discretíssimo jornalista a ser xingado e moído em palavras por uma horda de malandrinos a cinco ou seis passos dele surgida que cantavam e moviam seus braços em movimentos que não se pode classificar senão como bárbaros, e assim cantavam:
Grêmio TV
pior que o SBT !
-

@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
# My stupid introduction to Haskell
While I was writing my first small program on Haskell (really simple, but functional webapp) in December 2017 I only knew vaguely what was the style of things, some basic notions about functions, pure functions and so on (I've read about a third of [LYAH](http://learnyouahaskell.com/chapters)).
An enourmous amount of questions began to appear in my head while I read tutorials and documentation. Here I present some of the questions and the insights I got that solved them. Technically, they may be wrong, but they helped me advance in the matter, so I'm writing them down while I still can -- If I keep working with Haskell I'll probably get to know more and so my new insights will replace the previous ones, and the new ones won't be useful for total begginers anymore.
---
Here we go:
- **Why do modules have odd names?**
- modules are the things you import, like `Data.Time.Clock` or `Web.Scotty`.
- packages are the things you install, like 'time' or 'scotty'
- packages can contain any number of modules they like
- a module is just a collection of functions
- a package is just a collection of modules
- a package is just name you choose to associate your collection of modules with when you're publishing it to Hackage or whatever
- the module names you choose when you're writing a package can be anything, and these are the names people will have to `import` when they want to use you functions
- if you're from Javascript, Python or anything similar, you'll expect to be importing/writing the name of the package directly in your code, but in Haskell you'll actually be writing the name of the module, which may have nothing to do with the name of the package
- people choose things that make sense, like for `aeson` instead of `import Aeson` you'll be doing `import Data.Aeson`, `import Data.Aeson.Types` etc. why the `Data`? because they thought it would be nice. dealing with JSON is a form of dealing with data, so be it.
- you just have to check the package documentation to see which modules it exposes.
- **What is `data User = User { name :: Text }`?**
- a data type definition. means you'll have a function `User` that will take a Text parameter and output a `User` record or something like that.
- you can also have `Animal = Giraffe { color :: Text } | Human { name :: Text }`, so you'll have two functions, Giraffe and Human, each can take a different set of parameters, but they will both yield an Animal.
- then, in the functions that take an Animal parameter you must typematch to see if the animal is a giraffe or a human.
- **What is a monad?**
- a monad is a context, an environment.
- when you're in the context of a monad you can write imperative code.
- you do that when you use the keyword `do`.
- in the context of a monad, all values are prefixed by the monad type,
- thus, in the `IO` monad all `Text` is `IO Text` and so on.
- some monads have a relationship with others, so values from that monad can be turned into values from another monad and passed between context easily.
- for exampĺe, [scotty](https://www.stackage.org/haddock/lts-9.18/scotty-0.11.0/Web-Scotty.html)'s `ActionM` and `IO`. `ActionM` is just a subtype of `IO` or something like that.
- when you write imperative code inside a monad you can do assignments like `varname <- func x y`
- in these situations some transformation is done by the `<-`, I believe it is that the pure value returned by `func` is being transformed into a monad value. so if `func` returns `Text`, now varname is of type `IO Text` (if we're in the IO monad).
- so it will not work (and it can be confusing) if you try to concatenate functions like `varname <- transform $ func x y`, but you can somehow do
- `varname <- func x y`
- `othervarname <- transform varname`
- or you can do other fancy things you'll get familiar with later, like `varname <- fmap transform $ func x y`
- why? I don't know.
- **How do I deal with Maybe, Either or other crazy stuff?**
"ok, I understand what is a Maybe: it is a value that could be something or nothing. but how do I use that in my program?"
- you don't! you turn it into other thing. for example, you use [fromMaybe](http://hackage.haskell.org/package/base-4.10.1.0/docs/Data-Maybe.html#v:fromMaybe), a function that takes a default value and that's it. if your `Maybe` is `Just x` you get `x`, if it is `Nothing` you get the default value.
- using only that function you can already do whatever there is to be done with Maybes.
- you can also manipulate the values inside the `Maybe`, for example:
- if you have a `Maybe Person` and `Person` has a `name` which is `Text`, you can apply a function that turns `Maybe Person` into `Maybe Text` AND ONLY THEN you apply the default value (which would be something like the `"unnamed"`) and take the name from inside the `Maybe`.
- basically these things (`Maybe`, `Either`, `IO` also!) are just tags. they tag the value, and you can do things with the values inside them, or you can remove the values.
- besides the example above with Maybes and the `fromMaybe` function, you can also remove the values by using `case` -- for example:
- `case x of`
- `Left error -> error`
- `Right success -> success`
- `case y of`
- `Nothing -> "nothing!"`
- `Just value -> value`
- (in some cases I believe you can't remove the values, but in these cases you'll also don't need to)
- for example, for values tagged with the IO, you can't remove the IO and turn these values into pure values, but you don't need that, you can just take the value from the outside world, so it's a IO Text, apply functions that modify that value inside IO, then output the result to the user -- this is enough to make a complete program, any complete program.
- **JSON and interfaces (or instances?)**
- using [Aeson](https://hackage.haskell.org/package/aeson-1.2.3.0/docs/Data-Aeson.html) is easy, you just have to implement the `ToJSON` and `FromJSON` interfaces.
- "interface" is not the correct name, but I don't care.
- `ToJSON`, for example, requires a function named `toJSON`, so you do
- `instance ToJSON YourType where`
- `toJSON (YourType your type values) = object []` ... etc.
- I believe lots of things require interface implementation like this and it can be confusing, but once you know the mystery of implementing functions for interfaces everything is solved.
- `FromJSON` is a little less intuitive at the beggining, and I don't know if I did it correctly, but it is working here. Anyway, if you're trying to do that, I can only tell you to follow the types, copy examples from other places on the internet and don't care about the meaning of symbols.
## See also
* [Haskell Monoids](nostr:naddr1qqyrzcmrvcmrqwtpqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cktq992)
 @ a39d19ec:3d88f61e
2024-10-27 10:26:03**October's daily driver is the ana-digi Casio ABX-53 Twincept with module 1326. It features are world time, stopwatch, alarm and a databank for contacts.**  ## Design I have the gold/silver colored variant with a metal band. The watch has an analog clock and a floating display with the features listed above. Best thing is the "slider" mode that switches digital functions permanently. ## Storytime My log tells me that i bought the watch 6 years ago on a local flea market for close to nothing. It was in a bad condition and needed a new battery and some love. Sure enough it works fine since then. Most badass feature is that the analog hands are moved electronically not mechanically. Fun fact is that even my wife likes the floating display. First time she saw it I heard her say "Das ist echt cool", meaning "thats really cool".
@ a39d19ec:3d88f61e
2024-10-27 10:26:03**October's daily driver is the ana-digi Casio ABX-53 Twincept with module 1326. It features are world time, stopwatch, alarm and a databank for contacts.**  ## Design I have the gold/silver colored variant with a metal band. The watch has an analog clock and a floating display with the features listed above. Best thing is the "slider" mode that switches digital functions permanently. ## Storytime My log tells me that i bought the watch 6 years ago on a local flea market for close to nothing. It was in a bad condition and needed a new battery and some love. Sure enough it works fine since then. Most badass feature is that the analog hands are moved electronically not mechanically. Fun fact is that even my wife likes the floating display. First time she saw it I heard her say "Das ist echt cool", meaning "thats really cool". @ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also [addressing her Bill No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation. https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0 [(PT-BR version here)](https://www.eddieoz.com/drex-e-o-fim-do-dinheiro-fisico-no-brasil/) ## **What is a CBDC?** Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency. A prominent feature of CBDCs is their **programmability**. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area. In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously. ## **Practical Example: The Case of DREX During the Pandemic** To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, [the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence](https://youtu.be/cjUz2VEk4co?feature=shared&t=484&ref=eddieoz.com), limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice. To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government. ## **How Does China's Social Credit System Work?** Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, [including financial behavior, criminal record, social interactions, and even online activities](https://journals.sagepub.com/doi/full/10.1177/1461444819826402?ref=eddieoz.com). This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans. With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior. Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, [they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods](https://www.businessinsider.com/china-social-credit-system-punishments-and-rewards-explained-2018-4?ref=eddieoz.com), or even restricted to making transactions only at stores near their home. Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives. In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms. Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression. ## **DREX and Bill No. 3,341/2024** Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy ([Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG](https://www.camara.leg.br/proposicoesWeb/fichadetramitacao?idProposicao=2259342&fichaAmigavel=nao&ref=eddieoz.com)) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, [Julia drafted her bill, PL No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency. “The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.” ## **Risks and Individual Freedom** Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance. EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited. ## **The Relationship Between DREX and Pix** The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances. ## **International Precedents and Resistance to CBDC** The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations. Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning. ## **Bill No. 3,341/2024 and Popular Pressure** For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill. However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom. ## **What’s at Stake?** Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly. The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way. ## **A Call to Action** The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance. In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also [addressing her Bill No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation. https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0 [(PT-BR version here)](https://www.eddieoz.com/drex-e-o-fim-do-dinheiro-fisico-no-brasil/) ## **What is a CBDC?** Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency. A prominent feature of CBDCs is their **programmability**. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area. In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously. ## **Practical Example: The Case of DREX During the Pandemic** To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, [the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence](https://youtu.be/cjUz2VEk4co?feature=shared&t=484&ref=eddieoz.com), limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice. To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government. ## **How Does China's Social Credit System Work?** Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, [including financial behavior, criminal record, social interactions, and even online activities](https://journals.sagepub.com/doi/full/10.1177/1461444819826402?ref=eddieoz.com). This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans. With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior. Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, [they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods](https://www.businessinsider.com/china-social-credit-system-punishments-and-rewards-explained-2018-4?ref=eddieoz.com), or even restricted to making transactions only at stores near their home. Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives. In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms. Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression. ## **DREX and Bill No. 3,341/2024** Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy ([Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG](https://www.camara.leg.br/proposicoesWeb/fichadetramitacao?idProposicao=2259342&fichaAmigavel=nao&ref=eddieoz.com)) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, [Julia drafted her bill, PL No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency. “The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.” ## **Risks and Individual Freedom** Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance. EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited. ## **The Relationship Between DREX and Pix** The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances. ## **International Precedents and Resistance to CBDC** The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations. Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning. ## **Bill No. 3,341/2024 and Popular Pressure** For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill. However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom. ## **What’s at Stake?** Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly. The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way. ## **A Call to Action** The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance. In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values. @ 592295cf:413a0db9
2024-10-26 13:39:00[Week 21-10] I thinks that Saylor is on right, don't trust verify, is bullshit Bitcoin is a financial tool! I think it's good for me to get away from social media once a week. I could do things outside, like walking. Take pictures of the landscape. The weirdest thing is when the alarm calls you up in an hour. Fiatjaf wants a cache client. I feel like I can do it, I have the set to do it, but nostrudel is no longer working, so it's a little murky. Next nostrudel does not accept changes to settings (It works now!), so maybe i can think something. I want to make a corny chat, test, read this article. Nostr doesn't work with a vpn because relays don't know who you are. jokes aside, some clients have difficulties. ### **I couldn't take pictures of the landscape if I didn't take the wind blades.** Small local controversy. Missing the point of content creator. Simply for final user, Simply for the creator, new feature, no missing nothing. I'm trying to limit everything to writing for a week. I almost did. Maybe another week can do well. Meanwhile I updated apps like Amber and Voyager, coracle, nostrmo. The experiment continues with open vibe following the trending of Nostr. I'm following almost 120 npub. He'll stop, I don't know, possible he's already reached the limit. You still can't block words on the Nostr side of Open, strange thing. The app doesn't count the follow well, still some problem cleaning the cache seems that it doesn't need. After a while open and close and seems updated. I wanted to try open librarian, but I was busy sending fake zap on Nostr. This morning i try and It keeps giving me error 500 when I try to connect to a relay. I hate when a profile follows everyone indistinctly, why does everyone follow? and in voyage, I read with WoT setting, I probably have to do unfollow. There must be an indication in which not include the followers of this person in the web of trust, I would do it by default if you follow more than 600 people. WoT on Nostr Visualized [post on stackernews](https://stacker.news/items/739477)
@ 592295cf:413a0db9
2024-10-26 13:39:00[Week 21-10] I thinks that Saylor is on right, don't trust verify, is bullshit Bitcoin is a financial tool! I think it's good for me to get away from social media once a week. I could do things outside, like walking. Take pictures of the landscape. The weirdest thing is when the alarm calls you up in an hour. Fiatjaf wants a cache client. I feel like I can do it, I have the set to do it, but nostrudel is no longer working, so it's a little murky. Next nostrudel does not accept changes to settings (It works now!), so maybe i can think something. I want to make a corny chat, test, read this article. Nostr doesn't work with a vpn because relays don't know who you are. jokes aside, some clients have difficulties. ### **I couldn't take pictures of the landscape if I didn't take the wind blades.** Small local controversy. Missing the point of content creator. Simply for final user, Simply for the creator, new feature, no missing nothing. I'm trying to limit everything to writing for a week. I almost did. Maybe another week can do well. Meanwhile I updated apps like Amber and Voyager, coracle, nostrmo. The experiment continues with open vibe following the trending of Nostr. I'm following almost 120 npub. He'll stop, I don't know, possible he's already reached the limit. You still can't block words on the Nostr side of Open, strange thing. The app doesn't count the follow well, still some problem cleaning the cache seems that it doesn't need. After a while open and close and seems updated. I wanted to try open librarian, but I was busy sending fake zap on Nostr. This morning i try and It keeps giving me error 500 when I try to connect to a relay. I hate when a profile follows everyone indistinctly, why does everyone follow? and in voyage, I read with WoT setting, I probably have to do unfollow. There must be an indication in which not include the followers of this person in the web of trust, I would do it by default if you follow more than 600 people. WoT on Nostr Visualized [post on stackernews](https://stacker.news/items/739477) @ 8f69ac99:4f92f5fd
2024-10-25 09:49:56O recente relatório do Banco Central Europeu, [*As Consequências Distribucionais do Bitcoin*](https://papers.ssrn.com/sol3/Delivery.cfm/4985877.pdf?abstractid=4985877&mirid=1&type=2), recicla a velha narrativa de que o Bitcoin é um activo especulactivo que causa desigualdade de riqueza sem oferecer benefícios económicos tangíveis. Os autores, Ulrich Bindseil e Jürgen Schaaf, desfilam as críticas de sempre, afirmando que o Bitcoin falhou como sistema de pagamento global e que se transformou numa bolha, enriquecendo os primeiros utilizadores à custa da sociedade. Também lançam uma pitada de alarmismo ambiental e argumentam que o Bitcoin ameaça a democracia. Como era de esperar, o BCE continua apegado às mesmas concepções erradas que já foram desmentidas inúmeras vezes. O que este relatório não percebe, de forma espectacular, é que o Bitcoin não é apenas mais um activo; é uma tábua de salvação para aqueles desiludidos com os sistemas fiduciários inflacionários e governos corruptos. Ao longo desta análise, vamos desmontar os argumentos do BCE, expondo não só o seu profundo desconhecimento sobre o Bitcoin, mas também a ignorância gritante em relação ao seu potencial de conceder soberania financeira a milhões de pessoas em todo o mundo. O BCE retrata o Bitcoin como uma ferramenta elitista, mas ignora como as suas próprias políticas têm sistematicamente enriquecido alguns poucos à custa da maioria. Vamos então entrar no assunto. ### 1. **Deturpam o Papel do Bitcoin como Sistema de Pagamentos** > "O Bitcoin nunca foi usado em grande escala para transacções legais no mundo real." Que originalidade. Os autores descartam a utilidade de pagamento do Bitcoin com um gesto, mostrando que não compreendem a Lightning Network, que facilita transacções rápidas, baratas e escaláveis a nível global. Certamente, talvez os europeus ainda não estejam a comprar os seus cafés com Bitcoin, mas isso é irrelevante. O Bitcoin é uma tábua de salvação financeira em locais como El Salvador e em inúmeras outras regiões que sofrem com sistemas fiduciários em colapso. Esta visão eurocêntrica, como se todo o mundo partilhasse das mesmas condições económicas, reflecte uma total falta de perspectiva. Os autores seleccionam dados a dedo para encaixar na sua narrativa anti-Bitcoin, enquanto convenientemente ignoram os milhões que utilizam o Bitcoin para escapar à hiperinflação e a regimes autoritários. A afirmação de que o Bitcoin não é usado para transacções "legais" é não só enganosa, como revela a sua ignorância sobre as necessidades reais de quem vive fora da sua bolha privilegiada. --- ### 2. **Deturpam o Bitcoin como activo Especulactivo** > "O Bitcoin não gera qualquer fluxo de caixa (como o imobiliário), juros (como as obrigações) ou dividendos (como as ações)." Parabéns, BCE, acabaram de perder o ponto fulcral do Bitcoin. Esta afirmação mostra uma falta de entendimento fundamental do que torna o Bitcoin único. Ao contrário de imóveis ou obrigações, o Bitcoin é uma forma alternativa de dinheiro—não algum esquema de rendimento passivo. O valor do Bitcoin não depende de gerar dividendos ou juros, mas advém da sua escassez, descentralização e resistência à censura. Ao reduzir o Bitcoin a modelos de activos tradicionais, o BCE ignora o paradigma económico revolucionário que este oferece: uma escapatória aos sistemas fiduciários inflacionários, particularmente para os milhares de milhões de pessoas presas em sistemas financeiros corruptos. Ao tentar enquadrar o Bitcoin em modelos convencionais, os autores revelam a sua preguiça intelectual. A utilidade do Bitcoin reside no seu potencial como dinheiro sólido, e não como um veículo de investimento para especuladores atrás de rendimento. --- ### 3. **Deturpam os Custos Ambientais e Sociais da Mineração** > "A mineração de Bitcoin consome muita energia e causa danos ecológicos e sociais." Ah sim, o argumento gasto sobre o consumo energético. Enquanto a mineração de Bitcoin realmente requer energia, os autores omitem convenientemente os enormes avanços que a indústria fez em direcção à sustentabilidade. Cada vez mais, os mineradores de Bitcoin recorrem a fontes de energia renovável e, em alguns casos, estão até a ajudar a financiar infraestruturas de energia verde. A ironia aqui é que o BCE, uma instituição que fomenta políticas que inflam bolhas imobiliárias e de acções, de repente está preocupado com os custos sociais e ambientais. E mais, ignoram como a procura de energia barata por parte do Bitcoin incentiva realmente o desenvolvimento de soluções energéticas sustentáveis. Num mundo onde os sistemas fiduciários alimentam a ganância corporativa e a degradação ambiental, o Bitcoin está posicionado para impulsionar uma verdadeira inovação na energia verde. --- ### 4. **Visão Deturpada da Redistribuição de Riqueza** > "Os efeitos de riqueza do Bitcoin beneficiam os primeiros utilizadores à custa dos que chegam mais tarde e dos que não o possuem." Isto é pura comédia. Aparentemente, o BCE acabou de descobrir que os primeiros investidores em **qualquer** activo beneficiam mais do que os que chegam depois. Não é assim que os mercados funcionam? Os primeiros investidores em acções, imóveis e ouro beneficiam de forma desproporcional—mas, curiosamente, isto só se torna um problema quando se trata de Bitcoin. O que o BCE realmente teme é que o Bitcoin democratize a riqueza de uma maneira que eles não conseguem controlar. Com o Bitcoin, não precisas de acesso privilegiado para participar. Não precisas de um corretor _XPTO_ ou de permissão dos guardiões financeiros. Ao contrário das próprias políticas do BCE—concebidas para inflacionar a riqueza dos já ricos através de bolhas imobiliárias e do mercado de acções—Bitcoin oferece um campo de jogo nivelado para qualquer pessoa com uma ligação à internet. --- ### 5. **Sensacionalismo: a Ameaça à Democracia** > "O aumento perpétuo do preço do Bitcoin empobrece o resto da sociedade e põe em risco a democracia." Aqui, os autores entram no melodrama, avisando que o aumento do preço do Bitcoin põe em risco a democracia. É fascinante como ignoram a verdadeira ameaça à democracia: as suas próprias políticas inflacionárias. Na realidade, os sistemas fiduciários, através da inflação incessante e do _quantitative easing_, erodem sistematicamente a riqueza dos mais pobres e da classe média. Os ricos, com as suas carteiras de acções e imóveis, conseguem resistir à tempestade. Mas o trabalhador comum, cujo salário compra cada vez menos a cada ano, é esmagado. Se há algo que ameaça a democracia, é o poder descontrolado do BCE de desvalorizar a moeda que as pessoas usam para viver. Bitcoin, por outro lado, dá às pessoas uma reserva de valor incorruptível e descentralizada, imune aos caprichos dos banqueiros centrais. --- ### 6. **Percepção "Equivocada" da Escalabilidade do Bitcoin** > "As transações em Bitcoin na blockchain são lentas e caras." Esta crítica ignora a realidade do progresso tecnológico. As transacções on-chain de Bitcoin nunca foram pensadas para compras diárias—para isso é que serve a Lightning Network. Os autores agarram-se a esta crítica desactualizada, como se o Bitcoin fosse uma entidade estática que não evoluiu na última década. Soluções de segunda camada como a Lightning Network permitem transacções quase instantâneas e de baixo custo, tornando o Bitcoin escalável de maneiras que o BCE se recusa a reconhecer. Mas porque deixar que os factos estraguem uma boa história de medo? --- ### 7. **Ignoram o Impacto Económico Global do Bitcoin** > "O Bitcoin não tem casos de uso benéficos para a sociedade." Esta afirmação é tão limitada que é quase impressionante. A utilidade do Bitcoin não se trata de conveniência para os ocidentais comprarem café; trata-se de sobrevivência para as pessoas em países como a Venezuela, o Líbano ou a Nigéria. 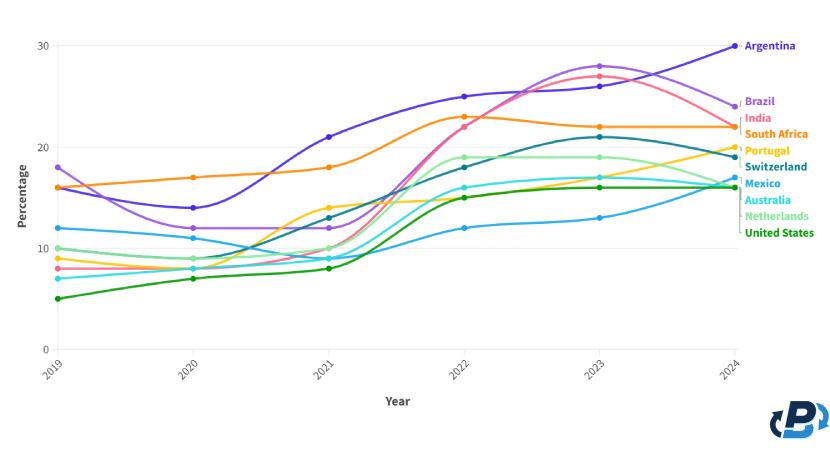 Quando as moedas locais colapsam e as pessoas não podem confiar nos seus bancos, o Bitcoin oferece uma saída. Ao descartar o impacto real de Bitcoin sobre os milhares de milhões (mais de metade da população mundial) de pessoas que vivem sob regimes opressivos e em hiperinflação, o BCE revela um embaraçoso viés ocidental e falta de empatia. O Bitcoin é mais do que apenas um activo alternativo, é uma tábua de salvação para pessoas em todo o mundo que sofrem com sistemas fiduciários falhados. --- ### Conclusão O relatório do BCE recicla críticas desactualizadas e já desmentidas, não conseguindo ver o panorama geral. Aplica modelos financeiros antigos a uma **nova forma de dinheiro**, ignorando o potencial de Bitcoin para democratizar o acesso a um sistema financeiro justo, descentralizado e incorruptível. Enquanto os bancos centrais, como o BCE, continuam a desvalorizar moedas e a inflacionar bolhas de activos (e parece que vem ai mais...), Bitcoin oferece às pessoas um caminho para a soberania financeira. O verdadeiro valor de Bitcoin não se encontra nas críticas superficiais e eurocêntricas do BCE. O seu valor reside na capacidade de fornecer liberdade financeira a indivíduos em todo o mundo, libertos da má gestão de governantes e banqueiros centrais. Se há algo que ameaça a democracia, é o historial do BCE de enriquecer alguns poucos à custa de muitos. Bitcoin, por outro lado, oferece um futuro mais justo—um onde são os indivíduos, e não as instituições, que têm o poder. Alguma literatura: - [Universidade de Cornell - Bitcoin pode impulsionar o desenvolvimento de energias renovaveis](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development) - [Aldeias em Africa com electricidade atraves de Bitcoin](https://gridlesscompute.com/2022/09/28/21st-century-villages/) - [Relatorio de 2023 sobre a Lightning Network da River](https://river.com/learn/files/river-lightning-report-2023.pdf) - [Adopcao de Bitcoin por Pais](https://plasbit.com/blog/bitcoin-adoption-by-country) --- _Photo by [Taras Chernus](https://unsplash.com/@chernus_tr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash]("https://unsplash.com/photos/man-in-teal-hoodie-with-i-love-you-text-euaivxORAm8?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_ #Bitcoin #BCE
@ 8f69ac99:4f92f5fd
2024-10-25 09:49:56O recente relatório do Banco Central Europeu, [*As Consequências Distribucionais do Bitcoin*](https://papers.ssrn.com/sol3/Delivery.cfm/4985877.pdf?abstractid=4985877&mirid=1&type=2), recicla a velha narrativa de que o Bitcoin é um activo especulactivo que causa desigualdade de riqueza sem oferecer benefícios económicos tangíveis. Os autores, Ulrich Bindseil e Jürgen Schaaf, desfilam as críticas de sempre, afirmando que o Bitcoin falhou como sistema de pagamento global e que se transformou numa bolha, enriquecendo os primeiros utilizadores à custa da sociedade. Também lançam uma pitada de alarmismo ambiental e argumentam que o Bitcoin ameaça a democracia. Como era de esperar, o BCE continua apegado às mesmas concepções erradas que já foram desmentidas inúmeras vezes. O que este relatório não percebe, de forma espectacular, é que o Bitcoin não é apenas mais um activo; é uma tábua de salvação para aqueles desiludidos com os sistemas fiduciários inflacionários e governos corruptos. Ao longo desta análise, vamos desmontar os argumentos do BCE, expondo não só o seu profundo desconhecimento sobre o Bitcoin, mas também a ignorância gritante em relação ao seu potencial de conceder soberania financeira a milhões de pessoas em todo o mundo. O BCE retrata o Bitcoin como uma ferramenta elitista, mas ignora como as suas próprias políticas têm sistematicamente enriquecido alguns poucos à custa da maioria. Vamos então entrar no assunto. ### 1. **Deturpam o Papel do Bitcoin como Sistema de Pagamentos** > "O Bitcoin nunca foi usado em grande escala para transacções legais no mundo real." Que originalidade. Os autores descartam a utilidade de pagamento do Bitcoin com um gesto, mostrando que não compreendem a Lightning Network, que facilita transacções rápidas, baratas e escaláveis a nível global. Certamente, talvez os europeus ainda não estejam a comprar os seus cafés com Bitcoin, mas isso é irrelevante. O Bitcoin é uma tábua de salvação financeira em locais como El Salvador e em inúmeras outras regiões que sofrem com sistemas fiduciários em colapso. Esta visão eurocêntrica, como se todo o mundo partilhasse das mesmas condições económicas, reflecte uma total falta de perspectiva. Os autores seleccionam dados a dedo para encaixar na sua narrativa anti-Bitcoin, enquanto convenientemente ignoram os milhões que utilizam o Bitcoin para escapar à hiperinflação e a regimes autoritários. A afirmação de que o Bitcoin não é usado para transacções "legais" é não só enganosa, como revela a sua ignorância sobre as necessidades reais de quem vive fora da sua bolha privilegiada. --- ### 2. **Deturpam o Bitcoin como activo Especulactivo** > "O Bitcoin não gera qualquer fluxo de caixa (como o imobiliário), juros (como as obrigações) ou dividendos (como as ações)." Parabéns, BCE, acabaram de perder o ponto fulcral do Bitcoin. Esta afirmação mostra uma falta de entendimento fundamental do que torna o Bitcoin único. Ao contrário de imóveis ou obrigações, o Bitcoin é uma forma alternativa de dinheiro—não algum esquema de rendimento passivo. O valor do Bitcoin não depende de gerar dividendos ou juros, mas advém da sua escassez, descentralização e resistência à censura. Ao reduzir o Bitcoin a modelos de activos tradicionais, o BCE ignora o paradigma económico revolucionário que este oferece: uma escapatória aos sistemas fiduciários inflacionários, particularmente para os milhares de milhões de pessoas presas em sistemas financeiros corruptos. Ao tentar enquadrar o Bitcoin em modelos convencionais, os autores revelam a sua preguiça intelectual. A utilidade do Bitcoin reside no seu potencial como dinheiro sólido, e não como um veículo de investimento para especuladores atrás de rendimento. --- ### 3. **Deturpam os Custos Ambientais e Sociais da Mineração** > "A mineração de Bitcoin consome muita energia e causa danos ecológicos e sociais." Ah sim, o argumento gasto sobre o consumo energético. Enquanto a mineração de Bitcoin realmente requer energia, os autores omitem convenientemente os enormes avanços que a indústria fez em direcção à sustentabilidade. Cada vez mais, os mineradores de Bitcoin recorrem a fontes de energia renovável e, em alguns casos, estão até a ajudar a financiar infraestruturas de energia verde. A ironia aqui é que o BCE, uma instituição que fomenta políticas que inflam bolhas imobiliárias e de acções, de repente está preocupado com os custos sociais e ambientais. E mais, ignoram como a procura de energia barata por parte do Bitcoin incentiva realmente o desenvolvimento de soluções energéticas sustentáveis. Num mundo onde os sistemas fiduciários alimentam a ganância corporativa e a degradação ambiental, o Bitcoin está posicionado para impulsionar uma verdadeira inovação na energia verde. --- ### 4. **Visão Deturpada da Redistribuição de Riqueza** > "Os efeitos de riqueza do Bitcoin beneficiam os primeiros utilizadores à custa dos que chegam mais tarde e dos que não o possuem." Isto é pura comédia. Aparentemente, o BCE acabou de descobrir que os primeiros investidores em **qualquer** activo beneficiam mais do que os que chegam depois. Não é assim que os mercados funcionam? Os primeiros investidores em acções, imóveis e ouro beneficiam de forma desproporcional—mas, curiosamente, isto só se torna um problema quando se trata de Bitcoin. O que o BCE realmente teme é que o Bitcoin democratize a riqueza de uma maneira que eles não conseguem controlar. Com o Bitcoin, não precisas de acesso privilegiado para participar. Não precisas de um corretor _XPTO_ ou de permissão dos guardiões financeiros. Ao contrário das próprias políticas do BCE—concebidas para inflacionar a riqueza dos já ricos através de bolhas imobiliárias e do mercado de acções—Bitcoin oferece um campo de jogo nivelado para qualquer pessoa com uma ligação à internet. --- ### 5. **Sensacionalismo: a Ameaça à Democracia** > "O aumento perpétuo do preço do Bitcoin empobrece o resto da sociedade e põe em risco a democracia." Aqui, os autores entram no melodrama, avisando que o aumento do preço do Bitcoin põe em risco a democracia. É fascinante como ignoram a verdadeira ameaça à democracia: as suas próprias políticas inflacionárias. Na realidade, os sistemas fiduciários, através da inflação incessante e do _quantitative easing_, erodem sistematicamente a riqueza dos mais pobres e da classe média. Os ricos, com as suas carteiras de acções e imóveis, conseguem resistir à tempestade. Mas o trabalhador comum, cujo salário compra cada vez menos a cada ano, é esmagado. Se há algo que ameaça a democracia, é o poder descontrolado do BCE de desvalorizar a moeda que as pessoas usam para viver. Bitcoin, por outro lado, dá às pessoas uma reserva de valor incorruptível e descentralizada, imune aos caprichos dos banqueiros centrais. --- ### 6. **Percepção "Equivocada" da Escalabilidade do Bitcoin** > "As transações em Bitcoin na blockchain são lentas e caras." Esta crítica ignora a realidade do progresso tecnológico. As transacções on-chain de Bitcoin nunca foram pensadas para compras diárias—para isso é que serve a Lightning Network. Os autores agarram-se a esta crítica desactualizada, como se o Bitcoin fosse uma entidade estática que não evoluiu na última década. Soluções de segunda camada como a Lightning Network permitem transacções quase instantâneas e de baixo custo, tornando o Bitcoin escalável de maneiras que o BCE se recusa a reconhecer. Mas porque deixar que os factos estraguem uma boa história de medo? --- ### 7. **Ignoram o Impacto Económico Global do Bitcoin** > "O Bitcoin não tem casos de uso benéficos para a sociedade." Esta afirmação é tão limitada que é quase impressionante. A utilidade do Bitcoin não se trata de conveniência para os ocidentais comprarem café; trata-se de sobrevivência para as pessoas em países como a Venezuela, o Líbano ou a Nigéria. 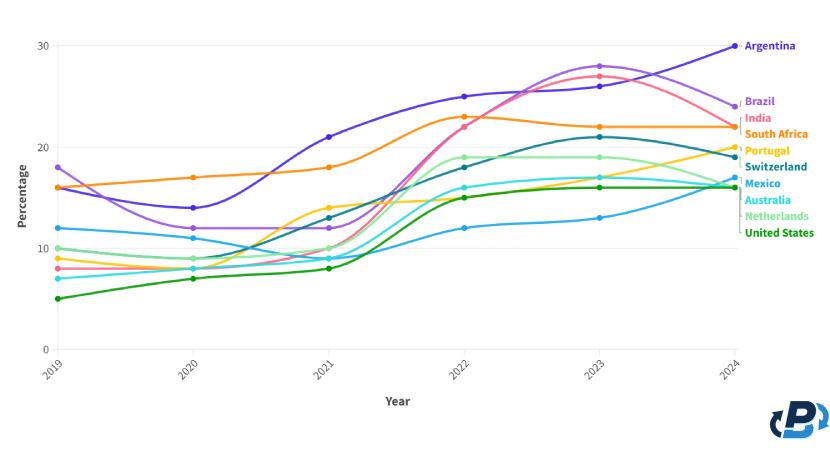 Quando as moedas locais colapsam e as pessoas não podem confiar nos seus bancos, o Bitcoin oferece uma saída. Ao descartar o impacto real de Bitcoin sobre os milhares de milhões (mais de metade da população mundial) de pessoas que vivem sob regimes opressivos e em hiperinflação, o BCE revela um embaraçoso viés ocidental e falta de empatia. O Bitcoin é mais do que apenas um activo alternativo, é uma tábua de salvação para pessoas em todo o mundo que sofrem com sistemas fiduciários falhados. --- ### Conclusão O relatório do BCE recicla críticas desactualizadas e já desmentidas, não conseguindo ver o panorama geral. Aplica modelos financeiros antigos a uma **nova forma de dinheiro**, ignorando o potencial de Bitcoin para democratizar o acesso a um sistema financeiro justo, descentralizado e incorruptível. Enquanto os bancos centrais, como o BCE, continuam a desvalorizar moedas e a inflacionar bolhas de activos (e parece que vem ai mais...), Bitcoin oferece às pessoas um caminho para a soberania financeira. O verdadeiro valor de Bitcoin não se encontra nas críticas superficiais e eurocêntricas do BCE. O seu valor reside na capacidade de fornecer liberdade financeira a indivíduos em todo o mundo, libertos da má gestão de governantes e banqueiros centrais. Se há algo que ameaça a democracia, é o historial do BCE de enriquecer alguns poucos à custa de muitos. Bitcoin, por outro lado, oferece um futuro mais justo—um onde são os indivíduos, e não as instituições, que têm o poder. Alguma literatura: - [Universidade de Cornell - Bitcoin pode impulsionar o desenvolvimento de energias renovaveis](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development) - [Aldeias em Africa com electricidade atraves de Bitcoin](https://gridlesscompute.com/2022/09/28/21st-century-villages/) - [Relatorio de 2023 sobre a Lightning Network da River](https://river.com/learn/files/river-lightning-report-2023.pdf) - [Adopcao de Bitcoin por Pais](https://plasbit.com/blog/bitcoin-adoption-by-country) --- _Photo by [Taras Chernus](https://unsplash.com/@chernus_tr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash]("https://unsplash.com/photos/man-in-teal-hoodie-with-i-love-you-text-euaivxORAm8?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_ #Bitcoin #BCE @ dd32f3e0:498f1df9
2024-10-25 01:42:06eyJfaWQiOiJkMmVkZDBkMy0yZmM3LTQxNWYtYTA5MC1iY2Q2ZDE2YTc2YjYiLCJwdWJsaWNLZXkiOiJkZDMyZjNlMDgzNDdlYTYzM2U2MzZkODlhMjMzOWQ0N2IyOTM2MWZkZTQ3MTZjZjNhZTBhMzhhYTQ5OGYxZGY5IiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJtYXJrZXRQcmljZSI6bnVsbCwiZml4ZWRQcmljZSI6MTUwLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6NTAwLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoibmljZSB0cmFkZXIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMTo0MjowNi4yNzBaIn0=
@ dd32f3e0:498f1df9
2024-10-25 01:42:06eyJfaWQiOiJkMmVkZDBkMy0yZmM3LTQxNWYtYTA5MC1iY2Q2ZDE2YTc2YjYiLCJwdWJsaWNLZXkiOiJkZDMyZjNlMDgzNDdlYTYzM2U2MzZkODlhMjMzOWQ0N2IyOTM2MWZkZTQ3MTZjZjNhZTBhMzhhYTQ5OGYxZGY5IiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJtYXJrZXRQcmljZSI6bnVsbCwiZml4ZWRQcmljZSI6MTUwLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6NTAwLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoibmljZSB0cmFkZXIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMTo0MjowNi4yNzBaIn0= @ 6f0ba1ef:58eb4351
2024-10-25 01:16:41eyJfaWQiOiIzMjFkMjkyNi0xOGUyLTRjYTgtOWIwYy0xNGMwNWExZDc4ZTAiLCJwdWJsaWNLZXkiOiI2ZjBiYTFlZjc4YjE3ZTVkMjNkMmVjZDlkYWNlNmJhMzBlODI1NzUxMGY0NmYxNjA0NGUyZjY5ZjU4ZWI0MzUxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MywibWFya2V0UHJpY2UiOjE1Ny40NiwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjoxMCwibWF4QW1vdW50IjoyMDAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiJ2ZXJ5IGZhc3QgYW5kIGVhc3kiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMToxNjo0MS41MDBaIn0=
@ 6f0ba1ef:58eb4351
2024-10-25 01:16:41eyJfaWQiOiIzMjFkMjkyNi0xOGUyLTRjYTgtOWIwYy0xNGMwNWExZDc4ZTAiLCJwdWJsaWNLZXkiOiI2ZjBiYTFlZjc4YjE3ZTVkMjNkMmVjZDlkYWNlNmJhMzBlODI1NzUxMGY0NmYxNjA0NGUyZjY5ZjU4ZWI0MzUxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MywibWFya2V0UHJpY2UiOjE1Ny40NiwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjoxMCwibWF4QW1vdW50IjoyMDAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiJ2ZXJ5IGZhc3QgYW5kIGVhc3kiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yNVQwMToxNjo0MS41MDBaIn0= @ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe *Denk Bar*! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt. Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen. Seit dem Start der *Denk Bar* vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. [Damals notierte ich](https://denkbar.substack.com/p/andreas-denk-bar-eroffnet): > «Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.» Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden. Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen [«inneren Totalschaden»](https://denkbar.substack.com/p/innerer-totalschaden) hatte ich mal für unsere Gesellschaften diagnostiziert. Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der [Gleichschaltung](https://denkbar.substack.com/p/warum-trotzdem-dieses-handeln), das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute. Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend. Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns. --- **Danke, dass du diesen Weg mit mir weitergehst!**
@ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe *Denk Bar*! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt. Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen. Seit dem Start der *Denk Bar* vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. [Damals notierte ich](https://denkbar.substack.com/p/andreas-denk-bar-eroffnet): > «Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.» Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden. Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen [«inneren Totalschaden»](https://denkbar.substack.com/p/innerer-totalschaden) hatte ich mal für unsere Gesellschaften diagnostiziert. Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der [Gleichschaltung](https://denkbar.substack.com/p/warum-trotzdem-dieses-handeln), das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute. Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend. Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns. --- **Danke, dass du diesen Weg mit mir weitergehst!** @ 6f0ba1ef:58eb4351
2024-10-22 23:31:47eyJfaWQiOiJjYmE4N2YyNS1jZjRkLTRkNzgtYmIwZS05YjNhNzA0MWVjNGIiLCJwdWJsaWNLZXkiOiI2ZjBiYTFlZjc4YjE3ZTVkMjNkMmVjZDlkYWNlNmJhMzBlODI1NzUxMGY0NmYxNjA0NGUyZjY5ZjU4ZWI0MzUxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwibWFya2V0UHJpY2UiOjE1Ny4zLCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwicGF5bWVudE1ldGhvZERldGFpbCI6IiIsIm1zZyI6IiIsImFjY291bnRJbmZvIjoiIiwiZm9yVHJ1c3RlZCI6Im5vIiwidmVyaWZpZWRFbWFpbFJlcXVpcmVkIjoibm8iLCJyZXF1aXJlRmVlZGJhY2tTY29yZSI6MCwiZmlyc3RUaW1lTGltaXRBc3NldCI6MCwicGF5bWVudFdpbmRvd01pbnV0ZXMiOjYwLCJoaWRkZW4iOmZhbHNlLCJiYW5uZWQiOmZhbHNlLCJ2ZXJpZmllZCI6dHJ1ZSwiYWRkZWQiOiIyMDI0LTEwLTIyVDIzOjMxOjQ3LjM5M1oifQ==
@ 6f0ba1ef:58eb4351
2024-10-22 23:31:47eyJfaWQiOiJjYmE4N2YyNS1jZjRkLTRkNzgtYmIwZS05YjNhNzA0MWVjNGIiLCJwdWJsaWNLZXkiOiI2ZjBiYTFlZjc4YjE3ZTVkMjNkMmVjZDlkYWNlNmJhMzBlODI1NzUxMGY0NmYxNjA0NGUyZjY5ZjU4ZWI0MzUxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwibWFya2V0UHJpY2UiOjE1Ny4zLCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwicGF5bWVudE1ldGhvZERldGFpbCI6IiIsIm1zZyI6IiIsImFjY291bnRJbmZvIjoiIiwiZm9yVHJ1c3RlZCI6Im5vIiwidmVyaWZpZWRFbWFpbFJlcXVpcmVkIjoibm8iLCJyZXF1aXJlRmVlZGJhY2tTY29yZSI6MCwiZmlyc3RUaW1lTGltaXRBc3NldCI6MCwicGF5bWVudFdpbmRvd01pbnV0ZXMiOjYwLCJoaWRkZW4iOmZhbHNlLCJiYW5uZWQiOmZhbHNlLCJ2ZXJpZmllZCI6dHJ1ZSwiYWRkZWQiOiIyMDI0LTEwLTIyVDIzOjMxOjQ3LjM5M1oifQ== @ 4ba8e86d:89d32de4
2024-10-22 23:20:59Usar um gerenciador de senhas pode resolver vários problemas, incluindo a dificuldade de criar senhas fortes e únicas, o risco de reutilização de senhas e a possibilidade de comprometimento de contas devido a senhas fracas ou roubadas. Com o uso de um gerenciador de senhas, o usuário pode criar senhas fortes e únicas para cada conta, sem precisar se preocupar em lembrar de todas elas. Além disso,um gerenciador de senhas pode ajudar a simplificar o processo de login, economizando tempo e reduzindo a frustração. O KeepassDX é uma versão do software de gerenciamento de senhas Keepass, desenvolvido originalmente por Dominik Reichl em 2003. O Keepass é um software gratuito e de código aberto para desktops, que permite que os usuários armazenem suas senhas em um banco de dados seguro, criptografado com algoritmos avançados. Em 2017, o desenvolvedor alemão Brian Pellmann criou o KeepassDX como uma versão para dispositivos móveis, com o objetivo de tornar mais fácil para os usuários gerenciarem suas senhas em smartphones e tablets. O KeepassDX foi criado a partir do código-fonte do Keepass e foi projetado para ser fácil de usar, seguro e personalizável. Pellmann adicionou várias funcionalidades novas ao KeepassDX, incluindo a capacidade de importar senhas de outros gerenciadores de senhas, a organização de senhas em categorias e a compatibilidade com serviços de armazenamento em nuvem para sincronização entre dispositivos. Algumas das funcionalidades do KeepassDX incluem a criação de senhas fortes e únicas, preenchimento automático de senhas, autenticação de dois fatores e organização de senhas por categorias. O KeepassDX também oferece uma ferramenta para importação de senhas de outros gerenciadores de senhas, o que torna a transição para o uso do KeepassDX mais fácil. Passo a passo instalação do aplicativo KeepassDX: 1. Baixe e instale o KeepassDX em seu dispositivo móvel https://play.google.com/store/apps/details?id=com.kunzisoft.keepass.free 2. Clique em [CRIAR NOVO BANCO DE DADOS] 3. Selecione o local do arquivo no meu caso é " transferência " Semelhante ao KeePassXC, o KeePassDX suporta o formato de banco de dados .kbdx (por exemplo, Passwords.kdbx) para armazenar senhas de contas importantes. Você deve salvar este arquivo em um local de fácil acesso para você, mas difícil de encontrar para outras pessoas que você não deseja visualizar as informações. Em particular, evite salvar seu arquivo de banco de dados em um serviço de armazenamento online, conectado às suas contas, pois pode ser acessado por outras pessoas. 4. Digite um nome para seu banco de dados Neste exemplo, " urso " nosso banco de dados como "urso.kdbx"; você pode escolher um nome de sua preferência. Você pode usar um nome que disfarce o arquivo e o torne menos óbvio para invasores que podem tentar acessar seu telefone e exigir que você desbloqueie o banco de dados. Também é possível alterar a "extensão" no final do nome do arquivo. Por exemplo, você pode nomear o banco de dados de senhas "Revoltadeatlas.pdf" "primainterior.jpg " e o sistema operacional geralmente dará ao arquivo um ícone de "aparência normal". Lembre-se de que, se você der ao seu banco de dados de senhas um nome que não termine em ".kdbx", não poderá abrir o arquivo diretamente. Em vez disso, você terá que iniciar o KeePassDX primeiro e, em seguida, abrir seu banco de dados clicando no botão "Abrir banco de dados existente". Felizmente, o KeePassDX lembra o último banco de dados que você abriu, então você não terá que fazer isso com frequência. https://github.com/Kunzisoft/KeePassDX
@ 4ba8e86d:89d32de4
2024-10-22 23:20:59Usar um gerenciador de senhas pode resolver vários problemas, incluindo a dificuldade de criar senhas fortes e únicas, o risco de reutilização de senhas e a possibilidade de comprometimento de contas devido a senhas fracas ou roubadas. Com o uso de um gerenciador de senhas, o usuário pode criar senhas fortes e únicas para cada conta, sem precisar se preocupar em lembrar de todas elas. Além disso,um gerenciador de senhas pode ajudar a simplificar o processo de login, economizando tempo e reduzindo a frustração. O KeepassDX é uma versão do software de gerenciamento de senhas Keepass, desenvolvido originalmente por Dominik Reichl em 2003. O Keepass é um software gratuito e de código aberto para desktops, que permite que os usuários armazenem suas senhas em um banco de dados seguro, criptografado com algoritmos avançados. Em 2017, o desenvolvedor alemão Brian Pellmann criou o KeepassDX como uma versão para dispositivos móveis, com o objetivo de tornar mais fácil para os usuários gerenciarem suas senhas em smartphones e tablets. O KeepassDX foi criado a partir do código-fonte do Keepass e foi projetado para ser fácil de usar, seguro e personalizável. Pellmann adicionou várias funcionalidades novas ao KeepassDX, incluindo a capacidade de importar senhas de outros gerenciadores de senhas, a organização de senhas em categorias e a compatibilidade com serviços de armazenamento em nuvem para sincronização entre dispositivos. Algumas das funcionalidades do KeepassDX incluem a criação de senhas fortes e únicas, preenchimento automático de senhas, autenticação de dois fatores e organização de senhas por categorias. O KeepassDX também oferece uma ferramenta para importação de senhas de outros gerenciadores de senhas, o que torna a transição para o uso do KeepassDX mais fácil. Passo a passo instalação do aplicativo KeepassDX: 1. Baixe e instale o KeepassDX em seu dispositivo móvel https://play.google.com/store/apps/details?id=com.kunzisoft.keepass.free 2. Clique em [CRIAR NOVO BANCO DE DADOS] 3. Selecione o local do arquivo no meu caso é " transferência " Semelhante ao KeePassXC, o KeePassDX suporta o formato de banco de dados .kbdx (por exemplo, Passwords.kdbx) para armazenar senhas de contas importantes. Você deve salvar este arquivo em um local de fácil acesso para você, mas difícil de encontrar para outras pessoas que você não deseja visualizar as informações. Em particular, evite salvar seu arquivo de banco de dados em um serviço de armazenamento online, conectado às suas contas, pois pode ser acessado por outras pessoas. 4. Digite um nome para seu banco de dados Neste exemplo, " urso " nosso banco de dados como "urso.kdbx"; você pode escolher um nome de sua preferência. Você pode usar um nome que disfarce o arquivo e o torne menos óbvio para invasores que podem tentar acessar seu telefone e exigir que você desbloqueie o banco de dados. Também é possível alterar a "extensão" no final do nome do arquivo. Por exemplo, você pode nomear o banco de dados de senhas "Revoltadeatlas.pdf" "primainterior.jpg " e o sistema operacional geralmente dará ao arquivo um ícone de "aparência normal". Lembre-se de que, se você der ao seu banco de dados de senhas um nome que não termine em ".kdbx", não poderá abrir o arquivo diretamente. Em vez disso, você terá que iniciar o KeePassDX primeiro e, em seguida, abrir seu banco de dados clicando no botão "Abrir banco de dados existente". Felizmente, o KeePassDX lembra o último banco de dados que você abriu, então você não terá que fazer isso com frequência. https://github.com/Kunzisoft/KeePassDX @ aa8de34f:a6ffe696
2024-10-22 19:36:06## Das Internet hat ein Problem. Nur wenige Leute wissen, dass dieses Problem existiert, aber hey, das liegt in der Natur ernsthafter, nicht offensichtlicher Probleme: Sie sind unsichtbar bis sie es nicht mehr sind. Das Problem mit dem Internet ist, dass Informationen frei sein wollen. Und wenn etwas FREI sein will wie in Freiheit, wird es mit genügend Zeit auch frei wie im Bier. Lass es mich erklären. ### Luftverschmutzung Jeden Tag verbrauchen wir ungeheure Mengen an Daten. Jede Sekunde jeder Minute strömen Bits und Bytes durch die Reihe von Leitungen die wir alle kennen und lieben: das Internet. Wir nehmen es als selbstverständlich hin und die meisten von uns halten das derzeitige Monetarisierungsmodell – sowie alle damit einhergehenden Übel – ebenfalls für selbstverständlich. Wir halten nur selten inne und denken über die seltsame Welt der Bits und Bytes nach. Wie wunderbar das alles ist, aber auch wie fremd. Wie es unser Leben bereits verändert hat und wie es unsere Zukunft weiter verändern wird. Woher kommen die Nullen und Einsen? Wie funktioniert das alles? Und vor allem: Wer zahlt dafür? Die Bits und Bytes, die durch unsere Glasfaserkabel rasen, sind so unsichtbar wie die Luft die wir atmen. Das ist keine schlechte Metapher wenn ich so darüber nachdenke. Solange wir keine Atemprobleme haben, müssen wir nicht anhalten und jedes einzelne Molekül, das wir einatmen, untersuchen. Ebenso lange wir keine Schwierigkeiten haben digitale Inhalte zu erstellen und zu konsumieren, brauchen wir auch nicht innezuhalten und all die verschiedenen Teile zu untersuchen, die unsere Aufmerksamkeitsökonomie am Laufen halten.\ **Aufmerksamkeitsökonomie**. Was für eine treffende Beschreibung. Wie wir inzwischen alle wissen sollten, ist das was wir konsumieren nicht umsonst, sondern wir bezahlen teuer dafür: mit unserer Aufmerksamkeit unter anderem. ### Paying Attention – mit Aufmerksamkeit bezahlen In der schnelllebigen Welt von heute muss man, um den Gewinn zu maximieren, die Aufmerksamkeit maximieren. Aber es ist eine eigentümliche, oberflächliche Art von Aufmerksamkeit. Es ist nicht die konzentrierte Art von Aufmerksamkeit, die tiefes Denken und sinnvolle Gespräche erfordern würden. Ich glaube, dass dies zumindest teilweise der Grund ist, warum viele Dinge so kaputt sind. Warum unser gesellschaftlicher Diskurs so zersplittert ist, unsere Politik so polarisiert, wir so gelähmt sind und unsere Analysen oft so oberflächlich sind wie unsere Wünsche.\ Die Aufmerksamkeitsökonomie hat uns fein säuberlich in Echokammern für persönliche Wahrheiten eingeteilt. Ironischerweise besteht die einzige Wahrheit die es wert ist, in der Aufmerksamkeitsökonomie verfolgt zu werden, darin, wie man eine maximale Anzahl von Menschen für eine maximale Zeitspanne maximal empört halten kann. Und das alles ohne dass die Teilnehmer merken, dass sie in einem selbst gewählten algorithmischen Gefängnis gefangen sind. ### Du bist das Produkt Die Redewendung „Wenn etwas kostenlos ist, bist du das Produkt“ kann nicht oft genug wiederholt werden. Aus dem einen oder anderen Grund erwarten wir, dass die meisten Dinge Online „kostenlos“ sind. Natürlich gibt es so etwas wie ein kostenloses Mittagessen nicht – nichts ist umsonst. Bei Online-Diensten werden deine Daten gesammelt und an den Meistbietenden verkauft, der in der Regel eine Werbeagentur oder eine Regierungsbehörde ist. Oder beides.\ Alle Big-Data-Unternehmen spionieren dich nicht nur aus, sondern nutzen auch eine Vielzahl von dunklen Mustern und unethischen Praktiken, um aus deinen Interaktionen auch den letzten Tropfen an Daten herauszuholen. Ob es sich dabei um den Facebook-Pixel, Google Analytics oder etwas anderes handelt, spielt keine Rolle. Du wirst nachverfolgt, überwacht und katalogisiert. Was du siehst, wie lange, zu welchen Zeiten, wie häufig und was du als Nächstes sehen wirst, wird sorgfältig von einem gewinnmaximierenden Algorithmus orchestriert. Profit für die Plattform, nicht für dich. Natürlich geht es in der Regel darum, dass alle davon profitieren: Nutzer, Urheber, Werbetreibende und die Plattformen gleichermaßen. Das evolutionäre Umfeld, das durch diese Anreizstrukturen geschaffen wird, führt jedoch häufig dazu, dass seichte, aufmerksamkeitsstarke und sensationslüsterne Schnipsel ausgewählt werden. Zum Zeitpunkt dieses Schreibens – Block 716.025 – ist der Inbegriff eines solchen Umfelds TikTok, eine videobasierte Dopaminmaschine, die dir das filmische Äquivalent von Heroin gemischt mit Crack zeigt. Harte Drogen für den Verstand, maßgeschneidert für deine besonderen Vorlieben. Eine wahrhaft verfluchte App. Leider unterscheiden sich die meisten dieser Plattformen nur in der Größe, nicht in der Art. ### Zulässige Meinungen „Es ist gar nicht so schlimm“, sagen wir uns. „Sieh dir all die nützlichen Informationen an!“, denken wir, während wir durch unsere Feeds scrollen, und füttern damit ungewollt die Maschine, die uns im Gegenzug mit Dopamin versorgt.\ Aber täuschen Sie sich nicht: Den verantwortlichen Unternehmen geht es nicht darum, uns mit nützlichen (oder wahrheitsgemäßen) Informationen zu versorgen. Es geht ihnen darum uns auszutricksen, damit wir die Maschine füttern.\ Wie könnte es anders sein? Man ist was man verfolgt, und man wird das worauf man optimiert wird. Aus Sicht der Plattform geht es um Klicks, nicht um Qualität. Auf den ersten Blick mag die Maximierung von Klicks und Verweildauer eine harmlose Sache sein. Schließlich muss man ja Geld verdienen um zu überleben. Es ist ja nur eine Anzeige. Wie schlimm kann es schon werden?\ Leider sind die Probleme, die damit einhergehen, zunächst unsichtbar. So wie Krebs für den Raucher unsichtbar ist, der gerade seine erste Zigarette geraucht hat, und Leberzirrhose für den Trinker unsichtbar ist, der gerade seinen ersten Drink zu sich genommen hat, so sind Deplatforming, Zensur, Polarisierung und Manipulation der öffentlichen Meinung für den Prosumenten unsichtbar, der gerade seine erste Anzeige auf einer geschlossenen Plattform gesehen hat. Wir können uns wahrscheinlich darauf einigen, dass wir das erste Inning (Stichwort Baseball) in dieser Frage hinter uns haben. Zensur ist die Norm, Deplatforming wird bejubelt, die Polarisierung ist auf einem Allzeithoch, und die öffentliche Meinung wird manuell und algorithmisch manipuliert wie nie zuvor.\ „Der Konsens ist, dass du zu dumm bist, um zu wissen was gut für dich ist und dass deine öffentliche Meinung zu unverschämt ist, um öffentlich geäußert zu werden. Schlimmer noch, es sollte gar nicht erst deine Meinung sein. Hier ist der Grund warum du falsch liegst. Hier ist eine Quelle die auf eine zulässige Meinung hinweist. Hier sind einige Experten, die mit uns übereinstimmen. Unsere intelligenten und hilfreichen Algorithmen haben die ganze Denkarbeit für dich erledigt, und sie liegen nie falsch. Genauso wenig wie die Experten.“\ Das ist die Welt, in der wir bereits leben. Es ist nicht erlaubt frei zu sprechen. Es ist nicht erlaubt frei zu denken. Du darfst dich nicht frei äußern. Dein Bild ist beleidigend und muss daher entfernt werden. Dein Meme ist zu nah an der Wahrheit oder zu kriminell lustig; deshalb müssen wir dich für ein oder zwei Wochen ins Twitter-Gefängnis stecken. Du sagst etwas mit dem wir nicht einverstanden sind; deshalb müssen wir dich auf Lebenszeit sperren – auch wenn du ein amtierender Präsident bist, wohlgemerkt. Du hast in einem Video das falsche Wort gesagt oder ein urheberrechtlich geschütztes Lied im Hintergrund abgespielt; deshalb müssen wir dir dein Einkommen wegnehmen. Du hast ein Bild von dir ohne Maske gepostet; deshalb müssen wir dich verbieten und den Behörden melden.1\ Die Tatsache, dass der obige Satz nicht mehr nur im Bereich der dystopischen Science-Fiction angesiedelt ist, sollte jeden beunruhigen. Aus dem Cyberspace entfernt – weil ich frei atmen wollte. Seltsame Zeiten. ### Evolutionärer Druck Wie ist es dazu gekommen? Wenn ich gezwungen wäre, eine kurze Antwort zu geben, würde ich Folgendes sagen: Wir sind von Protokollen zu Plattformen übergegangen, und Plattformen sind nur so gut wie ihre Anreize.\ Die Anreizstruktur der Plattformen, auf denen wir leben, ist die evolutionäre Umgebung, die das Überleben diktiert. Alles, was überleben will, muss sich daran orientieren. Das gilt natürlich für alle Bereiche der Wirtschaft. Nimm zum Beispiel Printmagazine. Wenn deine Zeitschrift kein schönes weibliches Gesicht auf der Titelseite hat, wird sie aus sehr menschlichen evolutionären Gründen nicht so oft gekauft werden wie die Zeitschriften, die ein solches Gesicht haben. Sie kann sich also nicht selbst reproduzieren und wird folglich sterben. Ähnlich verhält es sich mit einem Online-Nachrichtenportal, wenn es keine ausreichenden Werbeeinnahmen generiert und nicht in der Lage ist sich zu reproduzieren, wird es sterben. Aus diesem Grund hat jede Zeitschrift ein schönes weibliches Gesicht auf dem Cover. Und das ist der Grund, warum jede werbefinanzierte Online-Nachrichtenquelle zu Clickbait verkommt. <img src="https://cdn.satellite.earth/856054a1932c9fb70f9ae85bcb6d2d47330babb3cf7ac606c7861a09c8597f61.webp"> #### Eines dieser Gesichter ist anders als die anderen Das ist auch der Grund, warum sich Feed-basierte Empfehlungsmaschinen in Spielautomaten für deine Dopaminrezeptoren verwandeln. Je länger du an deinem Bildschirm klebst, desto mehr Werbung siehst du, desto mehr Einnahmen werden für die Plattform generiert. Das ist auch der Grund, warum die meisten YouTube-Kanäle zu 7- bis 15-minütigen Kurzvideos mit Vorschaubildern verkommen, die das Gesicht von jemandem zeigen, der gerade auf ein Legostück getreten ist. Kurz genug, um dich zu überzeugen es anzusehen, lang genug, um dich vergessen zu lassen, welches Video du dir eigentlich ansehen wolltest. Wie Ratten, die in hyperpersonalisierten Skinner-Boxen auf Knöpfe drücken, werden wir in Suchtzyklen konditioniert, um die Gewinne der Aktionäre zu maximieren. ### Profitmaximierung Plattformen sind Unternehmen und für Unternehmen gibt es Anreize die Gewinne der Aktionäre zu maximieren. Gegen Gewinne ist nichts einzuwenden und gegen Aktionäre ist auch nichts einzuwenden. Ich glaube jedoch, dass die Informationsrevolution, in der wir uns befinden, die evolutionäre Landschaft in zwei Teile gespalten hat. Nennen wir diese Landschaften „breit“ und „schmal“.\ Um die Gewinne durch breit angelegte Werbung zu maximieren, müssen Kontroversen und extreme Meinungen auf ein Minimum reduziert werden. Indem man den kleinsten gemeinsamen Nenner anspricht, kommen Politik und Zensur sofort ins Spiel. Umgekehrt müssen Kontroversen und extreme Meinungen maximiert werden, wenn die Gewinne durch schmale, gezielte Werbung erzielt werden sollen. Allein dadurch, dass verschiedenen Untergruppen unterschiedliche Informationen gezeigt werden, werden Polarisierung und Fragmentierung kontinuierlich verstärkt. <img src="https://cdn.satellite.earth/0d3a88d2700a3c26ed049b09d512a9a35dfc390bc95151e29d6950972114a00e.webp"> Allgemeine Kohäsion vs. algorithmische Spaltung Diese beiden Extreme sind zwei Seiten der gleichen Medaille. Es mag den Anschein haben, als ginge es um Kabelfernsehen gegen den algorithmischen Newsfeed, aber in Wirklichkeit handelt es sich um zwei unterschiedliche Ansätze, die dasselbe Ziel verfolgen: möglichst viele Menschen vor dem Bildschirm zu halten, damit sie mehr Werbung sehen. Das erste ist ein Beruhigungsmittel, das zweite ein Stimulans.\ Zugegeben, die obige Charakterisierung mag übertrieben sein, aber das Problem bleibt bestehen: Wenn wir nicht direkt für etwas bezahlen, bezahlen wir es indirekt, auf die eine oder andere Weise. Immer. Der Punkt ist der folgende: Plattformen für freie Meinungsäußerung können nicht existieren. Es kann nur Protokolle der freien Meinungsäußerung geben. Wenn jemand kontrollieren kann, was gesagt wird, wird jemand kontrollieren, was gesagt wird. Wenn du Inhalte überwachen, filtern und zensieren kannst, wirst du Inhalte überwachen, filtern und zensieren. Alle Plattformen werden mit diesem Problem konfrontiert, ganz gleich wie makellos ihre Absichten sind. Selbst wenn du dich anfangs als Plattform für freie Meinungsäußerung positionierst, wirst du auf lange Sicht gezwungen sein, einzugreifen und zu zensieren. Letztendlich wenn du für Inhalte, die du hostest oder übermittelst, vom Staat haftbar gemacht werden kannst, wirst du auch für Inhalte, die du hostest oder übermittelst, vom Staat haftbar gemacht werden. ### Selbstzensur Doch lange bevor die staatliche Zensur ihr hässliches Haupt erhebt, wird die abschreckende Wirkung der Selbstzensur zu spüren sein. Wenn andere wegen der Äußerung bestimmter Meinungen enttabuisiert und dämonisiert werden, werden die meisten Menschen sehr vorsichtig sein, diese Meinungen zu äußern. Bewusst und unbewusst bringen wir uns selbst langsam zum Schweigen. Wenn es um Selbstzensur geht, spielt auch die Werbung eine Rolle. Schließlich würdest du nicht die Hand beißen, die dich füttert, oder? Im schlimmsten Fall sagen dir die Werbetreibenden und Führungskräfte, was gesagt werden darf und was nicht. Sie werden dir sagen, welche Meinungen innerhalb und welche außerhalb des Overton-Fensters liegen. Und wenn sie es nicht tun, wirst du eine fundierte Vermutung anstellen und deine Aussagen entsprechend anpassen. ### Ein Problem und ein Paradoxon Zurück zum ursprünglichen Problem: Warum können wir Informationen nicht wie eine normale Ware verkaufen? Warum führt der einfache Ansatz – Inhalte hinter eine Bezahlschranke zu stellen – zu so schlechten Ergebnissen? Ich glaube, es gibt zwei Gründe, die ich das „MTX-Problem“ und das „DRM-Paradoxon“ nennen möchte. Das MTX-Problem, wobei MTX die Abkürzung für „mentale Transaktion“ (mental transaction) ist, bezieht sich auf das Problem der nicht reduzierbaren mentalen Transaktionskosten, die jeder Transaktion innewohnen. Jedes Mal, wenn du auf eine Bezahlschranke stößt, musst du eine bewusste Entscheidung treffen: „Möchte ich dafür bezahlen?“ Wie Szabo überzeugend darlegt, lautet die Antwort in den meisten Fällen, insbesondere wenn die Kosten gering sind, nein. Dafür gibt es keine technischen Gründe, sondern psychologische Gründe. Es stellt sich heraus, dass die Mühe, herauszufinden, ob sich diese Transaktion lohnt oder nicht – ein Prozess, der in deinem Kopf stattfindet – einfach zu groß ist. Wenn man über einen Mikrokauf nachdenken muss, sinkt die Wahrscheinlichkeit, dass man diesen Kauf tätigt, drastisch. Deshalb sind Flatrates und Abonnements der Renner: Man muss nur einmal darüber nachdenken. Bei den kleinsten Mikrotransaktionen ist dies sogar aus rein wirtschaftlicher Sicht der Fall. Wenn man einen Stundenlohn von 20 USD zugrunde legt und zwei Sekunden lang darüber nachdenkt: „Ist das 21 Sats wert?“, kostet das etwas mehr als 1¢, also mehr als der Preis der betreffenden Mikrotransaktion.\[2\] Das ist sowohl psychologisch als auch wirtschaftlich nicht machbar. Dies ist, kurz gesagt, das MTX-Problem. Aber das ist nicht das einzige Problem, das die Monetarisierung digitaler Inhalte belastet. Wie bereits erwähnt, gibt es auch das DRM-Paradoxon. DRM, kurz für „Digital-Rechte Management“ (Digital Rights Management), ist ein vergeblicher Versuch, das Kopieren von Informationen zu verhindern. Es sollte sich von selbst verstehen, dass nicht kopierbare Informationen ein Oxymoron sind, aber im Zeitalter von NFTs und vielem anderen Unsinn muss das leider ausdrücklich gesagt werden. Lass es mich also für dich buchstabieren: Man kann keine Informationen erstellen, die nicht kopiert werden können. Punkt. Oder, um es mit den Worten von Bruce Schneier zu sagen: „Der Versuch, digitale Dateien unkopierbar zu machen, ist wie der Versuch, Wasser nicht nass zu machen.“ Es liegt in der Natur der Sache, dass Informationen, wenn sie gelesen werden können, auch kopiert werden können – und zwar mit perfekter Genauigkeit. Kein noch so großer Trick oder künstliche Beschränkungen werden diese Tatsache ändern. Aus diesem Grund werden digitale Artefakte wie Filme und Musik immer kostenlos erhältlich sein. Es ist trivial für jemanden der Zugang zu diesen Artefakten hat, diese zu kopieren – zu Grenzkosten von nahezu Null, wohlgemerkt – und sie anderen zugänglich zu machen. Mit genügend Zeit und Popularität wird also jeder Film, jedes Lied und jedes Dokument für die\ Allgemeinheit kostenlos verfügbar sein. Die Natur der Information lässt kein anderes Ergebnis zu. Daher das Sprichwort: Information will frei sein. Obwohl der Versuch etwas zu schaffen das es nicht geben kann – Informationen die nicht kopiert werden können – an sich schon paradox ist, meine ich damit nicht das DRM-Paradoxon. Was ich meine, ist etwas viel Lustigeres. Es ist wiederum psychologischer, nicht technischer Natur. Das Paradoxon ist folgendes: Inhalte werden nur dann hinter einer Bezahlschranke bleiben, wenn sie schlecht sind. Wenn sie gut sind, wird sie jemand freilassen. Wir alle kennen das. Wenn ein Artikel tatsächlich lesenswert ist, wird jemand, der sich hinter der Bezahlschranke befindet, einen Screenshot davon machen und ihn in den sozialen Medien veröffentlichen. Wenn der Film es wert ist angeschaut zu werden, wird er auf verschiedenen Websites verfügbar sein, die Piratenschiffe als ihre Logos haben. Wenn der Song es wert ist gehört zu werden, wird er auf Streaming-Seiten kostenlos zur Verfügung stehen. Nur die schrecklichen Artikel, die obskursten Filme und die Lieder, bei denen einem die Ohren bluten, bleiben hinter Bezahlschranken. Daraus ergibt sich das Paradoxon: Inhalte bleiben nur dann hinter Bezahlschranken, wenn sie schlecht sind. Wenn sie gut sind, werden sie freigelassen. Ich persönlich glaube, dass das MTX-Problem ein größeres Problem darstellt als das DRM-Paradoxon. Die traditionelle Lösung für das MTX-Problem ist das Abonnementmodell, wie bei Netflix, Spotify, Amazon und so weiter. Das DRM-Paradoxon bleibt bestehen, aber es stellt sich heraus, dass dies kein Problem ist wenn man den „legitimen“ Zugang zu Informationen bequem genug gestaltet. Die Opportunitätskosten für das Herunterladen, Speichern, Pflegen und Warten einer privaten Liedersammlung sind für die meisten Menschen einfach zu hoch. Die bequemere Lösung ist für das verdammte Spotify-Abo zu bezahlen. Allerdings können wir bereits eines der Probleme erkennen, die mit dem Abonnementmodell verbunden sind. Der folgende Comic beschreibt es gut: Comic von /u/Hoppy_Doodle Die Verbreitung von Streaming-Plattformen zwingt dich dazu, ein Netflix-Abonnement, ein Amazon-Prime-Abonnement, ein Hulu-Abonnement, ein Disney-Plus-Abonnement, ein YouTube-Premium-Abonnement und so weiter abzuschließen. Und das war nur das Videostreaming. Den gleichen Abo-Zoo gibt es für Musik, Bücher, Spiele, Newsletter, Blogbeiträge usw. Und was ist die Lösung? ### Akzeptiere die Natur von Informationen Die Lösung beginnt mit Akzeptanz. Der Verkauf digitaler Inhalte auf herkömmliche, transaktionale Weise funktioniert nicht oder zumindest nicht sehr gut. Eine Transaktion mit einem digitalen Foto eines Apfels ist etwas ganz anderes als eine Transaktion mit einem physischen Apfel. George Bernard Shaw hat es am besten gesagt: „Wenn du einen Apfel hast und ich habe einen Apfel und wir tauschen diese Äpfel, dann haben wir beide immer noch jeweils einen Apfel. Aber wenn Sie eine Idee haben und ich eine Idee habe und wir diese Ideen austauschen, dann hat jeder von uns zwei Ideen.“ Da sich digitale Informationen wie eine Idee verhalten, gibt es keinen Grund, sie künstlich zu verknappen. Das gilt nicht nur in philosophischer, sondern auch technischer Hinsicht. Computer sind Kopiermaschinen. Das war schon immer so und wird auch so bleiben. Die einzige Möglichkeit, Informationen von einer Maschine auf eine andere zu übertragen, besteht darin, sie zu kopieren. Dies allein sollte die Sinnlosigkeit der Behandlung von Informationen als physische Objekte offenkundig machen. Wenn es um die Monetarisierung von Informationen im offenen Web geht, müssen wir unsere Denkweise mit der Natur der Information in Einklang bringen. Wie oben beschrieben, sind Informationen nicht knapp, leicht zu kopieren, leicht zu verändern und wollen frei sein. Ich glaube, dass das richtige Monetarisierungsmodell diese Werte respektieren und ähnliche Eigenschaften haben muss. Es muss offen, transparent, erweiterbar und nicht zuletzt völlig freiwillig sein. Dieses Modell hat einen Namen: Value-for-Value. ### Wiederbeleben der Straßenmusik Die Idee ist einfach, klingt aber radikal: Du stellst deine Inhalte kostenlos zur Verfügung, für jeden, ohne Zugangsbeschränkungen. Wenn die Menschen Spaß daran haben, wenn sie einen Nutzen daraus ziehen, dann machst du es den Menschen leicht etwas zurückzugeben.\ Es mag in der heutigen Zeit ungeheuerlich klingen, aber dieses Modell funktioniert seit Tausenden von Jahren. Es ist das Modell der Straßenkünstler, das Modell der Straßenmusikanten, das Modell des freiwilligen Gebens. Im Cyberspace stoßen wir jedoch nicht an die physischen Grenzen der traditionellen Straßenmusikanten. Digitale Inhalte lassen sich auf eine Art und Weise skalieren, wie es bei Darbietungen in der realen Welt nie der Fall sein wird. Das Value-for Value-Modell stellt das traditionelle Zahlungsmodell auf den Kopf. Traditionell folgt der Genuss der Bezahlung. Beim Value-for-Value-Ansatz folgt die Zahlung dem Genuss – freiwillig. Es steht dir frei, dem Straßenmusiker zuzuhören und weiterzugehen, aber – und das ist etwas was das Publikum intuitiv weiß – wenn du willst, dass die Musik weitergeht, solltest du ein paar Münzen in den Hut werfen. [Give value back](https://ts.dergigi.com/api/v1/invoices?storeId=3WkiYEG5DaQv7Ak5M2UjUi1pe5FFTPyNF1yAE9CVLNJn&orderId=V4V-busking&checkoutDesc=Value+for+Value%3A+Give+as+much+as+it+is+worth+to+you.¤cy=USD) Das Schöne an diesem Modell ist, dass es die Anreize neu ausrichtet. Man versucht nicht, die Klicks, die Verweildauer oder irgendeine andere der unzähligen Kennzahlen zu maximieren. Man will dem Publikum einen Mehrwert bieten, und das ist alles. Und wenn das Publikum einen Nutzen daraus gezogen hat, wird ein gewisser Prozentsatz etwas zurückgeben. Alles, was man tun muss, ist zu fragen. ### Eine wertvolle Alternative Wir stehen erst am Anfang dieses monumentalen Wandels. Ich hoffe, dass sich das Modell „Value for Value“ weiterhin als praktikable Alternative zu Werbung, Zensur, Deplatforming und Demonetisierung durchsetzen wird. Das Value-for-Value-Modell nimmt das „sie“ aus der Gleichung heraus. Sie filtern, sie zensieren, sie demonetisieren, sie deplatformieren. Es spielt nicht einmal eine Rolle, wer „sie“ sind. Wenn es „sie“ gibt, werden sie einen Weg finden, es zu versauen. Value-for-Value beseitigt „sie“ und überträgt dir die Verantwortung. Du bist der Herrscher im Reich des Einen, allein verantwortlich für deine Gedanken und deine Sprache. Wenn wir Befreiung (und Erlösung) im Cyberspace wollen, müssen wir dem Einzelnen wieder die Verantwortung übertragen. Wie immer gilt: Freiheit und Unabhängigkeit erfordern Verantwortung. In der besten aller Welten gibt es für die Schöpfer einen Anreiz, nichts anderes zu tun als zu erschaffen. Man bedient nur sich selbst und diejenigen, die an den Werken interessiert sind. Keine Mittelsmänner. Direkt, von Mensch zu Mensch, Value-for-Value. ### Was uns erwartet Zugegeben, heute ist es nicht gerade einfach, seine Infrastruktur selbst zu hosten. Es ist einschüchternd, einen eigenen Knotenpunkt (Node) zu betreiben, um Zahlungen auf selbständige Weise zu erhalten. Aber es wird nicht nur einfacher, es wird zunehmend notwendig. Wir müssen nicht nur alles einfacher machen, sondern uns auch des oben beschriebenen MTX-Problems bewusst sein. Jeder Schritt, der es schafft, die mentalen Transaktionskosten im Ökosystem der Wertschöpfung zu reduzieren, ist ein Schritt in die richtige Richtung. Die Wertfunktion von Podcasting 2.0 ist ein solcher Schritt. Sie ermöglicht und automatisiert Zahlungen im Minutentakt, ohne dass der Nutzer zusätzlich eingreifen muss. Sobald du eingerichtet bist, wird deine Geldbörse automatisch Zahlungen vornehmen. Ich glaube, dass weitere Iterationen dieser Idee in alle Medientypen integriert werden können, sei es Audio, Video, Bilder, das geschriebene Wort, und so weiter. Ich glaube, dass wir kurz vor der Protokollversion von Patreon stehen: alle Vorteile der Reduzierung der mentalen Transaktionskosten auf Null, ohne die Reibung und die Zensur, die einer plattformbasierten Lösung innewohnen. Ob es in Form von BOLT12 wiederkehrenden Zahlungen oder etwas ganz anderem kommen wird, bleibt abzuwarten. Ich bin jedoch zuversichtlich, dass dies zu gegebener Zeit der Fall sein wird. ### Schlussfolgerung Nicht nur unser Papiergeld ist kaputt, auch das Monetarisierungsmodell des Internets ist kaputt. Die werbebasierten Plattformen der heutigen Zeit sind auf Engagement durch Spaltung und Polarisierung optimiert und nutzen dunkle Muster und Sucht. Es wird nicht einfach sein, aus den Zwangsschleifen auszubrechen, die für uns eingerichtet wurden, aber dank des selbstverwalteten Tech-Stacks, der derzeit entsteht, gibt es eine praktikable Alternative: das Value-for-Value-Modell. Das „Straßenmusiker“-Monetarisierungsmodell (busking monetization model) hat in der Vergangenheit viele Jahrhunderte lang funktioniert, und dank Bitcoin und dem Lightning Network bin ich zuversichtlich, dass es auch in der Zukunft noch Jahrhunderte lang funktionieren wird. Wir sind fast am Ziel. Wir müssen nur noch herausfinden, wie wir den Hut richtig auf dem Boden positionieren und wo die besten Plätze in der Stadt sind, um sozusagen aufzutreten. Value-for-Value löst das DRM-Paradoxon in seiner Gesamtheit und wird – mit dem richtigen Maß an Automatisierung und vernünftigen Vorgaben – auch das MTX-Problem lösen. Wenn wir das richtig hinbekommen, können wir uns vielleicht aus dem evolutionären Überlebenskampf der Plattformen befreien und uns in das quasi unsterbliche Reich der Protokolle begeben. Es gibt viel zu erforschen, viele Werkzeuge zu entwickeln und viele vorgefasste Meinungen zu zerstören. Direkt vor unseren Augen vollzieht sich ein seismischer Wandel, und ich freue mich darauf, mit euch allen auf den Wellen zu reiten. Vorwärts marsch! --- *Dies ist ein übersetzter Gastbeitrag von Gigi aus seinem [Blog](https://dergigi.com/). Die geäußerten Meinungen sind ausschließlich seine eigenen und spiegeln nicht notwendigerweise die des Re-Publishers oder Aprycot Media wider. Quelle: https://aprycot.media/blog/freiheit-der-werte/#*
@ aa8de34f:a6ffe696
2024-10-22 19:36:06## Das Internet hat ein Problem. Nur wenige Leute wissen, dass dieses Problem existiert, aber hey, das liegt in der Natur ernsthafter, nicht offensichtlicher Probleme: Sie sind unsichtbar bis sie es nicht mehr sind. Das Problem mit dem Internet ist, dass Informationen frei sein wollen. Und wenn etwas FREI sein will wie in Freiheit, wird es mit genügend Zeit auch frei wie im Bier. Lass es mich erklären. ### Luftverschmutzung Jeden Tag verbrauchen wir ungeheure Mengen an Daten. Jede Sekunde jeder Minute strömen Bits und Bytes durch die Reihe von Leitungen die wir alle kennen und lieben: das Internet. Wir nehmen es als selbstverständlich hin und die meisten von uns halten das derzeitige Monetarisierungsmodell – sowie alle damit einhergehenden Übel – ebenfalls für selbstverständlich. Wir halten nur selten inne und denken über die seltsame Welt der Bits und Bytes nach. Wie wunderbar das alles ist, aber auch wie fremd. Wie es unser Leben bereits verändert hat und wie es unsere Zukunft weiter verändern wird. Woher kommen die Nullen und Einsen? Wie funktioniert das alles? Und vor allem: Wer zahlt dafür? Die Bits und Bytes, die durch unsere Glasfaserkabel rasen, sind so unsichtbar wie die Luft die wir atmen. Das ist keine schlechte Metapher wenn ich so darüber nachdenke. Solange wir keine Atemprobleme haben, müssen wir nicht anhalten und jedes einzelne Molekül, das wir einatmen, untersuchen. Ebenso lange wir keine Schwierigkeiten haben digitale Inhalte zu erstellen und zu konsumieren, brauchen wir auch nicht innezuhalten und all die verschiedenen Teile zu untersuchen, die unsere Aufmerksamkeitsökonomie am Laufen halten.\ **Aufmerksamkeitsökonomie**. Was für eine treffende Beschreibung. Wie wir inzwischen alle wissen sollten, ist das was wir konsumieren nicht umsonst, sondern wir bezahlen teuer dafür: mit unserer Aufmerksamkeit unter anderem. ### Paying Attention – mit Aufmerksamkeit bezahlen In der schnelllebigen Welt von heute muss man, um den Gewinn zu maximieren, die Aufmerksamkeit maximieren. Aber es ist eine eigentümliche, oberflächliche Art von Aufmerksamkeit. Es ist nicht die konzentrierte Art von Aufmerksamkeit, die tiefes Denken und sinnvolle Gespräche erfordern würden. Ich glaube, dass dies zumindest teilweise der Grund ist, warum viele Dinge so kaputt sind. Warum unser gesellschaftlicher Diskurs so zersplittert ist, unsere Politik so polarisiert, wir so gelähmt sind und unsere Analysen oft so oberflächlich sind wie unsere Wünsche.\ Die Aufmerksamkeitsökonomie hat uns fein säuberlich in Echokammern für persönliche Wahrheiten eingeteilt. Ironischerweise besteht die einzige Wahrheit die es wert ist, in der Aufmerksamkeitsökonomie verfolgt zu werden, darin, wie man eine maximale Anzahl von Menschen für eine maximale Zeitspanne maximal empört halten kann. Und das alles ohne dass die Teilnehmer merken, dass sie in einem selbst gewählten algorithmischen Gefängnis gefangen sind. ### Du bist das Produkt Die Redewendung „Wenn etwas kostenlos ist, bist du das Produkt“ kann nicht oft genug wiederholt werden. Aus dem einen oder anderen Grund erwarten wir, dass die meisten Dinge Online „kostenlos“ sind. Natürlich gibt es so etwas wie ein kostenloses Mittagessen nicht – nichts ist umsonst. Bei Online-Diensten werden deine Daten gesammelt und an den Meistbietenden verkauft, der in der Regel eine Werbeagentur oder eine Regierungsbehörde ist. Oder beides.\ Alle Big-Data-Unternehmen spionieren dich nicht nur aus, sondern nutzen auch eine Vielzahl von dunklen Mustern und unethischen Praktiken, um aus deinen Interaktionen auch den letzten Tropfen an Daten herauszuholen. Ob es sich dabei um den Facebook-Pixel, Google Analytics oder etwas anderes handelt, spielt keine Rolle. Du wirst nachverfolgt, überwacht und katalogisiert. Was du siehst, wie lange, zu welchen Zeiten, wie häufig und was du als Nächstes sehen wirst, wird sorgfältig von einem gewinnmaximierenden Algorithmus orchestriert. Profit für die Plattform, nicht für dich. Natürlich geht es in der Regel darum, dass alle davon profitieren: Nutzer, Urheber, Werbetreibende und die Plattformen gleichermaßen. Das evolutionäre Umfeld, das durch diese Anreizstrukturen geschaffen wird, führt jedoch häufig dazu, dass seichte, aufmerksamkeitsstarke und sensationslüsterne Schnipsel ausgewählt werden. Zum Zeitpunkt dieses Schreibens – Block 716.025 – ist der Inbegriff eines solchen Umfelds TikTok, eine videobasierte Dopaminmaschine, die dir das filmische Äquivalent von Heroin gemischt mit Crack zeigt. Harte Drogen für den Verstand, maßgeschneidert für deine besonderen Vorlieben. Eine wahrhaft verfluchte App. Leider unterscheiden sich die meisten dieser Plattformen nur in der Größe, nicht in der Art. ### Zulässige Meinungen „Es ist gar nicht so schlimm“, sagen wir uns. „Sieh dir all die nützlichen Informationen an!“, denken wir, während wir durch unsere Feeds scrollen, und füttern damit ungewollt die Maschine, die uns im Gegenzug mit Dopamin versorgt.\ Aber täuschen Sie sich nicht: Den verantwortlichen Unternehmen geht es nicht darum, uns mit nützlichen (oder wahrheitsgemäßen) Informationen zu versorgen. Es geht ihnen darum uns auszutricksen, damit wir die Maschine füttern.\ Wie könnte es anders sein? Man ist was man verfolgt, und man wird das worauf man optimiert wird. Aus Sicht der Plattform geht es um Klicks, nicht um Qualität. Auf den ersten Blick mag die Maximierung von Klicks und Verweildauer eine harmlose Sache sein. Schließlich muss man ja Geld verdienen um zu überleben. Es ist ja nur eine Anzeige. Wie schlimm kann es schon werden?\ Leider sind die Probleme, die damit einhergehen, zunächst unsichtbar. So wie Krebs für den Raucher unsichtbar ist, der gerade seine erste Zigarette geraucht hat, und Leberzirrhose für den Trinker unsichtbar ist, der gerade seinen ersten Drink zu sich genommen hat, so sind Deplatforming, Zensur, Polarisierung und Manipulation der öffentlichen Meinung für den Prosumenten unsichtbar, der gerade seine erste Anzeige auf einer geschlossenen Plattform gesehen hat. Wir können uns wahrscheinlich darauf einigen, dass wir das erste Inning (Stichwort Baseball) in dieser Frage hinter uns haben. Zensur ist die Norm, Deplatforming wird bejubelt, die Polarisierung ist auf einem Allzeithoch, und die öffentliche Meinung wird manuell und algorithmisch manipuliert wie nie zuvor.\ „Der Konsens ist, dass du zu dumm bist, um zu wissen was gut für dich ist und dass deine öffentliche Meinung zu unverschämt ist, um öffentlich geäußert zu werden. Schlimmer noch, es sollte gar nicht erst deine Meinung sein. Hier ist der Grund warum du falsch liegst. Hier ist eine Quelle die auf eine zulässige Meinung hinweist. Hier sind einige Experten, die mit uns übereinstimmen. Unsere intelligenten und hilfreichen Algorithmen haben die ganze Denkarbeit für dich erledigt, und sie liegen nie falsch. Genauso wenig wie die Experten.“\ Das ist die Welt, in der wir bereits leben. Es ist nicht erlaubt frei zu sprechen. Es ist nicht erlaubt frei zu denken. Du darfst dich nicht frei äußern. Dein Bild ist beleidigend und muss daher entfernt werden. Dein Meme ist zu nah an der Wahrheit oder zu kriminell lustig; deshalb müssen wir dich für ein oder zwei Wochen ins Twitter-Gefängnis stecken. Du sagst etwas mit dem wir nicht einverstanden sind; deshalb müssen wir dich auf Lebenszeit sperren – auch wenn du ein amtierender Präsident bist, wohlgemerkt. Du hast in einem Video das falsche Wort gesagt oder ein urheberrechtlich geschütztes Lied im Hintergrund abgespielt; deshalb müssen wir dir dein Einkommen wegnehmen. Du hast ein Bild von dir ohne Maske gepostet; deshalb müssen wir dich verbieten und den Behörden melden.1\ Die Tatsache, dass der obige Satz nicht mehr nur im Bereich der dystopischen Science-Fiction angesiedelt ist, sollte jeden beunruhigen. Aus dem Cyberspace entfernt – weil ich frei atmen wollte. Seltsame Zeiten. ### Evolutionärer Druck Wie ist es dazu gekommen? Wenn ich gezwungen wäre, eine kurze Antwort zu geben, würde ich Folgendes sagen: Wir sind von Protokollen zu Plattformen übergegangen, und Plattformen sind nur so gut wie ihre Anreize.\ Die Anreizstruktur der Plattformen, auf denen wir leben, ist die evolutionäre Umgebung, die das Überleben diktiert. Alles, was überleben will, muss sich daran orientieren. Das gilt natürlich für alle Bereiche der Wirtschaft. Nimm zum Beispiel Printmagazine. Wenn deine Zeitschrift kein schönes weibliches Gesicht auf der Titelseite hat, wird sie aus sehr menschlichen evolutionären Gründen nicht so oft gekauft werden wie die Zeitschriften, die ein solches Gesicht haben. Sie kann sich also nicht selbst reproduzieren und wird folglich sterben. Ähnlich verhält es sich mit einem Online-Nachrichtenportal, wenn es keine ausreichenden Werbeeinnahmen generiert und nicht in der Lage ist sich zu reproduzieren, wird es sterben. Aus diesem Grund hat jede Zeitschrift ein schönes weibliches Gesicht auf dem Cover. Und das ist der Grund, warum jede werbefinanzierte Online-Nachrichtenquelle zu Clickbait verkommt. <img src="https://cdn.satellite.earth/856054a1932c9fb70f9ae85bcb6d2d47330babb3cf7ac606c7861a09c8597f61.webp"> #### Eines dieser Gesichter ist anders als die anderen Das ist auch der Grund, warum sich Feed-basierte Empfehlungsmaschinen in Spielautomaten für deine Dopaminrezeptoren verwandeln. Je länger du an deinem Bildschirm klebst, desto mehr Werbung siehst du, desto mehr Einnahmen werden für die Plattform generiert. Das ist auch der Grund, warum die meisten YouTube-Kanäle zu 7- bis 15-minütigen Kurzvideos mit Vorschaubildern verkommen, die das Gesicht von jemandem zeigen, der gerade auf ein Legostück getreten ist. Kurz genug, um dich zu überzeugen es anzusehen, lang genug, um dich vergessen zu lassen, welches Video du dir eigentlich ansehen wolltest. Wie Ratten, die in hyperpersonalisierten Skinner-Boxen auf Knöpfe drücken, werden wir in Suchtzyklen konditioniert, um die Gewinne der Aktionäre zu maximieren. ### Profitmaximierung Plattformen sind Unternehmen und für Unternehmen gibt es Anreize die Gewinne der Aktionäre zu maximieren. Gegen Gewinne ist nichts einzuwenden und gegen Aktionäre ist auch nichts einzuwenden. Ich glaube jedoch, dass die Informationsrevolution, in der wir uns befinden, die evolutionäre Landschaft in zwei Teile gespalten hat. Nennen wir diese Landschaften „breit“ und „schmal“.\ Um die Gewinne durch breit angelegte Werbung zu maximieren, müssen Kontroversen und extreme Meinungen auf ein Minimum reduziert werden. Indem man den kleinsten gemeinsamen Nenner anspricht, kommen Politik und Zensur sofort ins Spiel. Umgekehrt müssen Kontroversen und extreme Meinungen maximiert werden, wenn die Gewinne durch schmale, gezielte Werbung erzielt werden sollen. Allein dadurch, dass verschiedenen Untergruppen unterschiedliche Informationen gezeigt werden, werden Polarisierung und Fragmentierung kontinuierlich verstärkt. <img src="https://cdn.satellite.earth/0d3a88d2700a3c26ed049b09d512a9a35dfc390bc95151e29d6950972114a00e.webp"> Allgemeine Kohäsion vs. algorithmische Spaltung Diese beiden Extreme sind zwei Seiten der gleichen Medaille. Es mag den Anschein haben, als ginge es um Kabelfernsehen gegen den algorithmischen Newsfeed, aber in Wirklichkeit handelt es sich um zwei unterschiedliche Ansätze, die dasselbe Ziel verfolgen: möglichst viele Menschen vor dem Bildschirm zu halten, damit sie mehr Werbung sehen. Das erste ist ein Beruhigungsmittel, das zweite ein Stimulans.\ Zugegeben, die obige Charakterisierung mag übertrieben sein, aber das Problem bleibt bestehen: Wenn wir nicht direkt für etwas bezahlen, bezahlen wir es indirekt, auf die eine oder andere Weise. Immer. Der Punkt ist der folgende: Plattformen für freie Meinungsäußerung können nicht existieren. Es kann nur Protokolle der freien Meinungsäußerung geben. Wenn jemand kontrollieren kann, was gesagt wird, wird jemand kontrollieren, was gesagt wird. Wenn du Inhalte überwachen, filtern und zensieren kannst, wirst du Inhalte überwachen, filtern und zensieren. Alle Plattformen werden mit diesem Problem konfrontiert, ganz gleich wie makellos ihre Absichten sind. Selbst wenn du dich anfangs als Plattform für freie Meinungsäußerung positionierst, wirst du auf lange Sicht gezwungen sein, einzugreifen und zu zensieren. Letztendlich wenn du für Inhalte, die du hostest oder übermittelst, vom Staat haftbar gemacht werden kannst, wirst du auch für Inhalte, die du hostest oder übermittelst, vom Staat haftbar gemacht werden. ### Selbstzensur Doch lange bevor die staatliche Zensur ihr hässliches Haupt erhebt, wird die abschreckende Wirkung der Selbstzensur zu spüren sein. Wenn andere wegen der Äußerung bestimmter Meinungen enttabuisiert und dämonisiert werden, werden die meisten Menschen sehr vorsichtig sein, diese Meinungen zu äußern. Bewusst und unbewusst bringen wir uns selbst langsam zum Schweigen. Wenn es um Selbstzensur geht, spielt auch die Werbung eine Rolle. Schließlich würdest du nicht die Hand beißen, die dich füttert, oder? Im schlimmsten Fall sagen dir die Werbetreibenden und Führungskräfte, was gesagt werden darf und was nicht. Sie werden dir sagen, welche Meinungen innerhalb und welche außerhalb des Overton-Fensters liegen. Und wenn sie es nicht tun, wirst du eine fundierte Vermutung anstellen und deine Aussagen entsprechend anpassen. ### Ein Problem und ein Paradoxon Zurück zum ursprünglichen Problem: Warum können wir Informationen nicht wie eine normale Ware verkaufen? Warum führt der einfache Ansatz – Inhalte hinter eine Bezahlschranke zu stellen – zu so schlechten Ergebnissen? Ich glaube, es gibt zwei Gründe, die ich das „MTX-Problem“ und das „DRM-Paradoxon“ nennen möchte. Das MTX-Problem, wobei MTX die Abkürzung für „mentale Transaktion“ (mental transaction) ist, bezieht sich auf das Problem der nicht reduzierbaren mentalen Transaktionskosten, die jeder Transaktion innewohnen. Jedes Mal, wenn du auf eine Bezahlschranke stößt, musst du eine bewusste Entscheidung treffen: „Möchte ich dafür bezahlen?“ Wie Szabo überzeugend darlegt, lautet die Antwort in den meisten Fällen, insbesondere wenn die Kosten gering sind, nein. Dafür gibt es keine technischen Gründe, sondern psychologische Gründe. Es stellt sich heraus, dass die Mühe, herauszufinden, ob sich diese Transaktion lohnt oder nicht – ein Prozess, der in deinem Kopf stattfindet – einfach zu groß ist. Wenn man über einen Mikrokauf nachdenken muss, sinkt die Wahrscheinlichkeit, dass man diesen Kauf tätigt, drastisch. Deshalb sind Flatrates und Abonnements der Renner: Man muss nur einmal darüber nachdenken. Bei den kleinsten Mikrotransaktionen ist dies sogar aus rein wirtschaftlicher Sicht der Fall. Wenn man einen Stundenlohn von 20 USD zugrunde legt und zwei Sekunden lang darüber nachdenkt: „Ist das 21 Sats wert?“, kostet das etwas mehr als 1¢, also mehr als der Preis der betreffenden Mikrotransaktion.\[2\] Das ist sowohl psychologisch als auch wirtschaftlich nicht machbar. Dies ist, kurz gesagt, das MTX-Problem. Aber das ist nicht das einzige Problem, das die Monetarisierung digitaler Inhalte belastet. Wie bereits erwähnt, gibt es auch das DRM-Paradoxon. DRM, kurz für „Digital-Rechte Management“ (Digital Rights Management), ist ein vergeblicher Versuch, das Kopieren von Informationen zu verhindern. Es sollte sich von selbst verstehen, dass nicht kopierbare Informationen ein Oxymoron sind, aber im Zeitalter von NFTs und vielem anderen Unsinn muss das leider ausdrücklich gesagt werden. Lass es mich also für dich buchstabieren: Man kann keine Informationen erstellen, die nicht kopiert werden können. Punkt. Oder, um es mit den Worten von Bruce Schneier zu sagen: „Der Versuch, digitale Dateien unkopierbar zu machen, ist wie der Versuch, Wasser nicht nass zu machen.“ Es liegt in der Natur der Sache, dass Informationen, wenn sie gelesen werden können, auch kopiert werden können – und zwar mit perfekter Genauigkeit. Kein noch so großer Trick oder künstliche Beschränkungen werden diese Tatsache ändern. Aus diesem Grund werden digitale Artefakte wie Filme und Musik immer kostenlos erhältlich sein. Es ist trivial für jemanden der Zugang zu diesen Artefakten hat, diese zu kopieren – zu Grenzkosten von nahezu Null, wohlgemerkt – und sie anderen zugänglich zu machen. Mit genügend Zeit und Popularität wird also jeder Film, jedes Lied und jedes Dokument für die\ Allgemeinheit kostenlos verfügbar sein. Die Natur der Information lässt kein anderes Ergebnis zu. Daher das Sprichwort: Information will frei sein. Obwohl der Versuch etwas zu schaffen das es nicht geben kann – Informationen die nicht kopiert werden können – an sich schon paradox ist, meine ich damit nicht das DRM-Paradoxon. Was ich meine, ist etwas viel Lustigeres. Es ist wiederum psychologischer, nicht technischer Natur. Das Paradoxon ist folgendes: Inhalte werden nur dann hinter einer Bezahlschranke bleiben, wenn sie schlecht sind. Wenn sie gut sind, wird sie jemand freilassen. Wir alle kennen das. Wenn ein Artikel tatsächlich lesenswert ist, wird jemand, der sich hinter der Bezahlschranke befindet, einen Screenshot davon machen und ihn in den sozialen Medien veröffentlichen. Wenn der Film es wert ist angeschaut zu werden, wird er auf verschiedenen Websites verfügbar sein, die Piratenschiffe als ihre Logos haben. Wenn der Song es wert ist gehört zu werden, wird er auf Streaming-Seiten kostenlos zur Verfügung stehen. Nur die schrecklichen Artikel, die obskursten Filme und die Lieder, bei denen einem die Ohren bluten, bleiben hinter Bezahlschranken. Daraus ergibt sich das Paradoxon: Inhalte bleiben nur dann hinter Bezahlschranken, wenn sie schlecht sind. Wenn sie gut sind, werden sie freigelassen. Ich persönlich glaube, dass das MTX-Problem ein größeres Problem darstellt als das DRM-Paradoxon. Die traditionelle Lösung für das MTX-Problem ist das Abonnementmodell, wie bei Netflix, Spotify, Amazon und so weiter. Das DRM-Paradoxon bleibt bestehen, aber es stellt sich heraus, dass dies kein Problem ist wenn man den „legitimen“ Zugang zu Informationen bequem genug gestaltet. Die Opportunitätskosten für das Herunterladen, Speichern, Pflegen und Warten einer privaten Liedersammlung sind für die meisten Menschen einfach zu hoch. Die bequemere Lösung ist für das verdammte Spotify-Abo zu bezahlen. Allerdings können wir bereits eines der Probleme erkennen, die mit dem Abonnementmodell verbunden sind. Der folgende Comic beschreibt es gut: Comic von /u/Hoppy_Doodle Die Verbreitung von Streaming-Plattformen zwingt dich dazu, ein Netflix-Abonnement, ein Amazon-Prime-Abonnement, ein Hulu-Abonnement, ein Disney-Plus-Abonnement, ein YouTube-Premium-Abonnement und so weiter abzuschließen. Und das war nur das Videostreaming. Den gleichen Abo-Zoo gibt es für Musik, Bücher, Spiele, Newsletter, Blogbeiträge usw. Und was ist die Lösung? ### Akzeptiere die Natur von Informationen Die Lösung beginnt mit Akzeptanz. Der Verkauf digitaler Inhalte auf herkömmliche, transaktionale Weise funktioniert nicht oder zumindest nicht sehr gut. Eine Transaktion mit einem digitalen Foto eines Apfels ist etwas ganz anderes als eine Transaktion mit einem physischen Apfel. George Bernard Shaw hat es am besten gesagt: „Wenn du einen Apfel hast und ich habe einen Apfel und wir tauschen diese Äpfel, dann haben wir beide immer noch jeweils einen Apfel. Aber wenn Sie eine Idee haben und ich eine Idee habe und wir diese Ideen austauschen, dann hat jeder von uns zwei Ideen.“ Da sich digitale Informationen wie eine Idee verhalten, gibt es keinen Grund, sie künstlich zu verknappen. Das gilt nicht nur in philosophischer, sondern auch technischer Hinsicht. Computer sind Kopiermaschinen. Das war schon immer so und wird auch so bleiben. Die einzige Möglichkeit, Informationen von einer Maschine auf eine andere zu übertragen, besteht darin, sie zu kopieren. Dies allein sollte die Sinnlosigkeit der Behandlung von Informationen als physische Objekte offenkundig machen. Wenn es um die Monetarisierung von Informationen im offenen Web geht, müssen wir unsere Denkweise mit der Natur der Information in Einklang bringen. Wie oben beschrieben, sind Informationen nicht knapp, leicht zu kopieren, leicht zu verändern und wollen frei sein. Ich glaube, dass das richtige Monetarisierungsmodell diese Werte respektieren und ähnliche Eigenschaften haben muss. Es muss offen, transparent, erweiterbar und nicht zuletzt völlig freiwillig sein. Dieses Modell hat einen Namen: Value-for-Value. ### Wiederbeleben der Straßenmusik Die Idee ist einfach, klingt aber radikal: Du stellst deine Inhalte kostenlos zur Verfügung, für jeden, ohne Zugangsbeschränkungen. Wenn die Menschen Spaß daran haben, wenn sie einen Nutzen daraus ziehen, dann machst du es den Menschen leicht etwas zurückzugeben.\ Es mag in der heutigen Zeit ungeheuerlich klingen, aber dieses Modell funktioniert seit Tausenden von Jahren. Es ist das Modell der Straßenkünstler, das Modell der Straßenmusikanten, das Modell des freiwilligen Gebens. Im Cyberspace stoßen wir jedoch nicht an die physischen Grenzen der traditionellen Straßenmusikanten. Digitale Inhalte lassen sich auf eine Art und Weise skalieren, wie es bei Darbietungen in der realen Welt nie der Fall sein wird. Das Value-for Value-Modell stellt das traditionelle Zahlungsmodell auf den Kopf. Traditionell folgt der Genuss der Bezahlung. Beim Value-for-Value-Ansatz folgt die Zahlung dem Genuss – freiwillig. Es steht dir frei, dem Straßenmusiker zuzuhören und weiterzugehen, aber – und das ist etwas was das Publikum intuitiv weiß – wenn du willst, dass die Musik weitergeht, solltest du ein paar Münzen in den Hut werfen. [Give value back](https://ts.dergigi.com/api/v1/invoices?storeId=3WkiYEG5DaQv7Ak5M2UjUi1pe5FFTPyNF1yAE9CVLNJn&orderId=V4V-busking&checkoutDesc=Value+for+Value%3A+Give+as+much+as+it+is+worth+to+you.¤cy=USD) Das Schöne an diesem Modell ist, dass es die Anreize neu ausrichtet. Man versucht nicht, die Klicks, die Verweildauer oder irgendeine andere der unzähligen Kennzahlen zu maximieren. Man will dem Publikum einen Mehrwert bieten, und das ist alles. Und wenn das Publikum einen Nutzen daraus gezogen hat, wird ein gewisser Prozentsatz etwas zurückgeben. Alles, was man tun muss, ist zu fragen. ### Eine wertvolle Alternative Wir stehen erst am Anfang dieses monumentalen Wandels. Ich hoffe, dass sich das Modell „Value for Value“ weiterhin als praktikable Alternative zu Werbung, Zensur, Deplatforming und Demonetisierung durchsetzen wird. Das Value-for-Value-Modell nimmt das „sie“ aus der Gleichung heraus. Sie filtern, sie zensieren, sie demonetisieren, sie deplatformieren. Es spielt nicht einmal eine Rolle, wer „sie“ sind. Wenn es „sie“ gibt, werden sie einen Weg finden, es zu versauen. Value-for-Value beseitigt „sie“ und überträgt dir die Verantwortung. Du bist der Herrscher im Reich des Einen, allein verantwortlich für deine Gedanken und deine Sprache. Wenn wir Befreiung (und Erlösung) im Cyberspace wollen, müssen wir dem Einzelnen wieder die Verantwortung übertragen. Wie immer gilt: Freiheit und Unabhängigkeit erfordern Verantwortung. In der besten aller Welten gibt es für die Schöpfer einen Anreiz, nichts anderes zu tun als zu erschaffen. Man bedient nur sich selbst und diejenigen, die an den Werken interessiert sind. Keine Mittelsmänner. Direkt, von Mensch zu Mensch, Value-for-Value. ### Was uns erwartet Zugegeben, heute ist es nicht gerade einfach, seine Infrastruktur selbst zu hosten. Es ist einschüchternd, einen eigenen Knotenpunkt (Node) zu betreiben, um Zahlungen auf selbständige Weise zu erhalten. Aber es wird nicht nur einfacher, es wird zunehmend notwendig. Wir müssen nicht nur alles einfacher machen, sondern uns auch des oben beschriebenen MTX-Problems bewusst sein. Jeder Schritt, der es schafft, die mentalen Transaktionskosten im Ökosystem der Wertschöpfung zu reduzieren, ist ein Schritt in die richtige Richtung. Die Wertfunktion von Podcasting 2.0 ist ein solcher Schritt. Sie ermöglicht und automatisiert Zahlungen im Minutentakt, ohne dass der Nutzer zusätzlich eingreifen muss. Sobald du eingerichtet bist, wird deine Geldbörse automatisch Zahlungen vornehmen. Ich glaube, dass weitere Iterationen dieser Idee in alle Medientypen integriert werden können, sei es Audio, Video, Bilder, das geschriebene Wort, und so weiter. Ich glaube, dass wir kurz vor der Protokollversion von Patreon stehen: alle Vorteile der Reduzierung der mentalen Transaktionskosten auf Null, ohne die Reibung und die Zensur, die einer plattformbasierten Lösung innewohnen. Ob es in Form von BOLT12 wiederkehrenden Zahlungen oder etwas ganz anderem kommen wird, bleibt abzuwarten. Ich bin jedoch zuversichtlich, dass dies zu gegebener Zeit der Fall sein wird. ### Schlussfolgerung Nicht nur unser Papiergeld ist kaputt, auch das Monetarisierungsmodell des Internets ist kaputt. Die werbebasierten Plattformen der heutigen Zeit sind auf Engagement durch Spaltung und Polarisierung optimiert und nutzen dunkle Muster und Sucht. Es wird nicht einfach sein, aus den Zwangsschleifen auszubrechen, die für uns eingerichtet wurden, aber dank des selbstverwalteten Tech-Stacks, der derzeit entsteht, gibt es eine praktikable Alternative: das Value-for-Value-Modell. Das „Straßenmusiker“-Monetarisierungsmodell (busking monetization model) hat in der Vergangenheit viele Jahrhunderte lang funktioniert, und dank Bitcoin und dem Lightning Network bin ich zuversichtlich, dass es auch in der Zukunft noch Jahrhunderte lang funktionieren wird. Wir sind fast am Ziel. Wir müssen nur noch herausfinden, wie wir den Hut richtig auf dem Boden positionieren und wo die besten Plätze in der Stadt sind, um sozusagen aufzutreten. Value-for-Value löst das DRM-Paradoxon in seiner Gesamtheit und wird – mit dem richtigen Maß an Automatisierung und vernünftigen Vorgaben – auch das MTX-Problem lösen. Wenn wir das richtig hinbekommen, können wir uns vielleicht aus dem evolutionären Überlebenskampf der Plattformen befreien und uns in das quasi unsterbliche Reich der Protokolle begeben. Es gibt viel zu erforschen, viele Werkzeuge zu entwickeln und viele vorgefasste Meinungen zu zerstören. Direkt vor unseren Augen vollzieht sich ein seismischer Wandel, und ich freue mich darauf, mit euch allen auf den Wellen zu reiten. Vorwärts marsch! --- *Dies ist ein übersetzter Gastbeitrag von Gigi aus seinem [Blog](https://dergigi.com/). Die geäußerten Meinungen sind ausschließlich seine eigenen und spiegeln nicht notwendigerweise die des Re-Publishers oder Aprycot Media wider. Quelle: https://aprycot.media/blog/freiheit-der-werte/#* @ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication. https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de ### **Sections:** - **Introduction** - **What Is Chat Control?** - **Why Is the EU Pushing for Chat Control?** - **The Privacy Concerns and Risks** - **The Technical Debate: Encryption and Backdoors** - **Global Reactions and the Debate in Europe** - **Possible Consequences for Messaging Services** - **What Happens Next? The Future of Chat Control** - **Conclusion** --- ### **What Is Chat Control?** "Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns. At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content. #### **Origins of the Proposal** The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms. #### **How Messaging Services Work** Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors. <img src="https://blossom.primal.net/31ace3b729fb9f6b4de286686f31a71db6dd7e3a363f868e1255a6f287eb0b94.png"> #### **Key Elements of Chat Control** - **Automated Content Scanning**: Service providers would use algorithms to scan messages for illegal content. - **Circumvention of Encryption**: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security. - **Mandatory Reporting**: If illegal content is detected, providers would be required to report it to authorities. - **Broad Applicability**: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms. #### **Why It Matters** Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought. --- ### **Why Is the EU Pushing for Chat Control?** The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms. #### **Protecting Children and Preventing Crime** One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes. Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety. #### **Legal Context and Legislative Drivers** The push for Chat Control is rooted in several legislative initiatives: - **ePrivacy Directive**: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances. - **Temporary Derogation**: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive. - **Regulation Proposals**: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications. #### **Balancing Security and Privacy** EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections. However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as: - **Targeted Scanning**: Focusing on specific threats rather than broad, indiscriminate monitoring. - **Judicial Oversight**: Requiring court orders or oversight for accessing private communications. - **Data Protection Safeguards**: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed. <img src="https://blossom.primal.net/9533aedc9f83564d53633eac1a6d431d1e311028a478dd4b7f3a59b2c449e95a.png"> #### **The Urgency Behind the Push** High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked. #### **Criticism and Controversy** Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose. --- ### **The Privacy Concerns and Risks** While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications. #### **Infringement on Privacy Rights** At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms. #### **Erosion of End-to-End Encryption** End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats. #### **Concerns from Privacy Advocates** Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences: - **Security Risks**: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime. - **Global Implications**: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy. - **Ineffectiveness Against Crime**: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens. <img src="https://blossom.primal.net/51722887ebf55c827cc20bcfade3ea9b3628265b7fa3547504b2fff45f34f175.png"> #### **Potential for Government Overreach** There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent. #### **Real-World Implications for Users** - **False Positives**: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users. - **Chilling Effect**: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse. - **Data Misuse**: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information. #### **Legal and Ethical Concerns** Privacy advocates also highlight potential conflicts with existing laws and ethical standards: - **Violation of Fundamental Rights**: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression. - **Questionable Effectiveness**: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users. #### **Opposition from Member States and Organizations** Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences. --- ### **The Technical Debate: Encryption and Backdoors** The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures. #### **What Is End-to-End Encryption (E2EE)?** End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content. - **Security Assurance**: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private. - **Widespread Use**: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data. #### **How Chat Control Affects Encryption** Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to: - **Introduce Backdoors**: Create a means for third parties (including the service provider or authorities) to access encrypted messages. - **Client-Side Scanning**: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE. #### **The Risks of Weakening Encryption** **1. Compromised Security for All Users** Introducing backdoors or client-side scanning tools can create vulnerabilities: - **Exploitable Gaps**: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches. - **Universal Impact**: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk. **2. Undermining Trust in Digital Services** - **User Confidence**: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms. - **Business Implications**: Companies relying on secure communications might face increased risks, affecting economic activities. **3. Ineffectiveness Against Skilled Adversaries** - **Alternative Methods**: Criminals might shift to other encrypted channels or develop new ways to avoid detection. - **False Sense of Security**: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected. #### **Signal’s Response and Stance** Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals: - **Refusal to Weaken Encryption**: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards. - **Advocacy for Privacy**: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age. #### **Understanding Backdoors** A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems: - **Security Vulnerabilities**: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments. - **Ethical Concerns**: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications. <img src="https://blossom.primal.net/67f45fd79ccdb7e2e2ecdc56297207dc0d1d073acb216857b6165b3bf9906997.png"> #### **The Slippery Slope Argument** Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent: - **Expanded Surveillance**: Once in place, these measures could be extended to monitor other types of content beyond the original scope. - **Erosion of Rights**: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time. #### **Potential Technological Alternatives** Some suggest that it's possible to fight illegal content without undermining encryption: - **Metadata Analysis**: Focusing on patterns of communication rather than content. - **Enhanced Reporting Mechanisms**: Encouraging users to report illegal content voluntarily. - **Investing in Law Enforcement Capabilities**: Strengthening traditional investigative methods without compromising digital security. #### The technical community largely agrees that weakening encryption is not the solution: - **Consensus on Security**: Strong encryption is essential for the safety and privacy of all internet users. - **Call for Dialogue**: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights. --- ### **Global Reactions and the Debate in Europe** The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values. #### **Support for Chat Control** Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that: - **Enhanced Security**: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes. - **Responsibility of Service Providers**: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities. - **Public Safety Priorities**: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy. #### **Opposition within the EU** Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach. **Germany** - **Stance**: Germany has been one of the most vocal opponents of the proposed measures. - **Reasons**: - **Constitutional Concerns**: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications. - **Security Risks**: Weakening encryption is seen as a threat to cybersecurity. - **Legal Challenges**: Potential conflicts with national laws protecting personal data and communication secrecy. **Netherlands** - **Recent Developments**: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy. - **Arguments**: - **Effectiveness Doubts**: Skepticism about the actual effectiveness of the measures in combating crime. - **Negative Impact on Privacy**: Concerns about mass surveillance and the infringement of citizens' rights. Table reference: Patrick Breyer - Chat Control in 23 September 2024 #### **Privacy Advocacy Groups** **European Digital Rights (EDRi)** - **Role**: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment. - **Position**: - **Strong Opposition**: EDRi argues that Chat Control is incompatible with fundamental rights. - **Awareness Campaigns**: Engaging in public campaigns to inform citizens about the potential risks. - **Policy Engagement**: Lobbying policymakers to consider alternative approaches that respect privacy. **Politicians and Activists** **Patrick Breyer** - **Background**: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party. - **Actions**: - **Advocacy**: Actively campaigning against Chat Control through speeches, articles, and legislative efforts. - **Public Outreach**: Using social media and public events to raise awareness. - **Legal Expertise**: Highlighting the legal inconsistencies and potential violations of EU law. #### **Global Reactions** **International Organizations** - **Human Rights Watch and Amnesty International**: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider. **Technology Companies** - **Global Tech Firms**: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust. - **Industry Associations**: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness. <img src="https://blossom.primal.net/e761aa2dd240a1a2e7d943565ccbda427b5a8054bf4e6e17c946711ab6370d5d.png"> #### **The Broader Debate** The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include: - **Legal Precedents**: How the EU's decision might influence laws and regulations in other countries. - **Digital Sovereignty**: The desire of nations to control digital spaces within their borders. - **Civil Liberties**: The importance of protecting freedoms in the face of technological advancements. #### **Public Opinion** - **Diverse Views**: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all. - **Awareness Levels**: Many people are still unaware of the potential changes, highlighting the need for public education on the issue. #### The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society. --- ### **Possible Consequences for Messaging Services** The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication. #### **Impact on Encrypted Messaging Services** **Signal and Similar Platforms** - **Compliance Challenges**: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles. - **Operational Decisions**: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features. #### **Potential Blocking or Limiting of Services** - **Regulatory Enforcement**: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU. - **Access Restrictions**: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements. #### **Effects on Smaller Providers** - **Resource Constraints**: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market. - **Innovation Stifling**: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector. <img src="https://blossom.primal.net/60a9cad69b45cc3ded1d1759312e49a57b3aa997db62e36016f40642943be5e9.png"> #### **User Experience and Trust** - **Privacy Concerns**: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement. - **Migration to Unregulated Platforms**: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks. #### **Technical and Security Implications** - **Increased Vulnerabilities**: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches. - **Global Security Risks**: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders. #### **Impact on Businesses and Professional Communications** - **Confidentiality Issues**: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services. - **Compliance Complexity**: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens. #### **Economic Consequences** - **Market Fragmentation**: Divergent regulations could lead to a fragmented market, with different versions of services for different regions. - **Loss of Revenue**: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance. #### **Responses from Service Providers** - **Legal Challenges**: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights. - **Policy Advocacy**: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control. #### **Possible Adaptations** - **Technological Innovation**: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain. - **Transparency Measures**: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy. #### The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape. --- ### **What Happens Next? The Future of Chat Control** The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union. #### **Current Status of Legislation** - **Ongoing Negotiations**: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders. - **Timeline**: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay. #### **Key Influencing Factors** **1. Legal Challenges and Compliance with EU Law** - **Fundamental Rights Assessment**: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression. - **Court Scrutiny**: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control. **2. Technological Feasibility** - **Development of Privacy-Preserving Technologies**: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies. - **Implementation Challenges**: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures. **3. Political Dynamics** - **Member State Positions**: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations. - **Public Opinion and Advocacy**: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections. **4. Industry Responses** - **Negotiations with Service Providers**: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed. - **Potential for Self-Regulation**: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning. #### **Possible Scenarios** **Optimistic Outcome:** - **Balanced Regulation**: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight. **Pessimistic Outcome:** - **Adoption of Strict Measures**: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market. **Middle Ground:** - **Incremental Implementation**: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact. #### **How to Stay Informed and Protect Your Privacy** - **Follow Reputable Sources**: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments. - **Engage in the Dialogue**: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy. - **Utilize Secure Practices**: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security. <img src="https://blossom.primal.net/1e2c0cd70d88629c54ac84f928ab107f08f698d2c7f0df511277fb44c1480f0a.png"> #### **The Global Perspective** - **International Implications**: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against. - **Collaboration Opportunities**: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats. #### **Looking Ahead** The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders. As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world. --- ### **Conclusion** The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns. Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits. The potential consequences of implementing Chat Control are far-reaching: - **Erosion of Trust**: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online. - **Security Vulnerabilities**: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks. - **Stifling Innovation**: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry. - **Global Implications**: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse. As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values. The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free. In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world. <img src="https://blossom.primal.net/d3f07d8bc7a49ac291f14eb449879462c76ae407abbe728ddc6f93e11fabe11d.png"> --- Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future. ## Read more: - https://www.patrick-breyer.de/en/posts/chat-control/ - https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/ - https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/ - https://signal.org/blog/pdfs/ndss-keynote.pdf - https://tuta.com/blog/germany-stop-chat-control - https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal - https://mullvad.net/en/why-privacy-matters
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication. https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de ### **Sections:** - **Introduction** - **What Is Chat Control?** - **Why Is the EU Pushing for Chat Control?** - **The Privacy Concerns and Risks** - **The Technical Debate: Encryption and Backdoors** - **Global Reactions and the Debate in Europe** - **Possible Consequences for Messaging Services** - **What Happens Next? The Future of Chat Control** - **Conclusion** --- ### **What Is Chat Control?** "Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns. At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content. #### **Origins of the Proposal** The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms. #### **How Messaging Services Work** Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors. <img src="https://blossom.primal.net/31ace3b729fb9f6b4de286686f31a71db6dd7e3a363f868e1255a6f287eb0b94.png"> #### **Key Elements of Chat Control** - **Automated Content Scanning**: Service providers would use algorithms to scan messages for illegal content. - **Circumvention of Encryption**: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security. - **Mandatory Reporting**: If illegal content is detected, providers would be required to report it to authorities. - **Broad Applicability**: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms. #### **Why It Matters** Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought. --- ### **Why Is the EU Pushing for Chat Control?** The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms. #### **Protecting Children and Preventing Crime** One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes. Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety. #### **Legal Context and Legislative Drivers** The push for Chat Control is rooted in several legislative initiatives: - **ePrivacy Directive**: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances. - **Temporary Derogation**: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive. - **Regulation Proposals**: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications. #### **Balancing Security and Privacy** EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections. However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as: - **Targeted Scanning**: Focusing on specific threats rather than broad, indiscriminate monitoring. - **Judicial Oversight**: Requiring court orders or oversight for accessing private communications. - **Data Protection Safeguards**: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed. <img src="https://blossom.primal.net/9533aedc9f83564d53633eac1a6d431d1e311028a478dd4b7f3a59b2c449e95a.png"> #### **The Urgency Behind the Push** High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked. #### **Criticism and Controversy** Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose. --- ### **The Privacy Concerns and Risks** While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications. #### **Infringement on Privacy Rights** At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms. #### **Erosion of End-to-End Encryption** End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats. #### **Concerns from Privacy Advocates** Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences: - **Security Risks**: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime. - **Global Implications**: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy. - **Ineffectiveness Against Crime**: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens. <img src="https://blossom.primal.net/51722887ebf55c827cc20bcfade3ea9b3628265b7fa3547504b2fff45f34f175.png"> #### **Potential for Government Overreach** There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent. #### **Real-World Implications for Users** - **False Positives**: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users. - **Chilling Effect**: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse. - **Data Misuse**: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information. #### **Legal and Ethical Concerns** Privacy advocates also highlight potential conflicts with existing laws and ethical standards: - **Violation of Fundamental Rights**: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression. - **Questionable Effectiveness**: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users. #### **Opposition from Member States and Organizations** Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences. --- ### **The Technical Debate: Encryption and Backdoors** The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures. #### **What Is End-to-End Encryption (E2EE)?** End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content. - **Security Assurance**: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private. - **Widespread Use**: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data. #### **How Chat Control Affects Encryption** Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to: - **Introduce Backdoors**: Create a means for third parties (including the service provider or authorities) to access encrypted messages. - **Client-Side Scanning**: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE. #### **The Risks of Weakening Encryption** **1. Compromised Security for All Users** Introducing backdoors or client-side scanning tools can create vulnerabilities: - **Exploitable Gaps**: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches. - **Universal Impact**: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk. **2. Undermining Trust in Digital Services** - **User Confidence**: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms. - **Business Implications**: Companies relying on secure communications might face increased risks, affecting economic activities. **3. Ineffectiveness Against Skilled Adversaries** - **Alternative Methods**: Criminals might shift to other encrypted channels or develop new ways to avoid detection. - **False Sense of Security**: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected. #### **Signal’s Response and Stance** Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals: - **Refusal to Weaken Encryption**: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards. - **Advocacy for Privacy**: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age. #### **Understanding Backdoors** A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems: - **Security Vulnerabilities**: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments. - **Ethical Concerns**: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications. <img src="https://blossom.primal.net/67f45fd79ccdb7e2e2ecdc56297207dc0d1d073acb216857b6165b3bf9906997.png"> #### **The Slippery Slope Argument** Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent: - **Expanded Surveillance**: Once in place, these measures could be extended to monitor other types of content beyond the original scope. - **Erosion of Rights**: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time. #### **Potential Technological Alternatives** Some suggest that it's possible to fight illegal content without undermining encryption: - **Metadata Analysis**: Focusing on patterns of communication rather than content. - **Enhanced Reporting Mechanisms**: Encouraging users to report illegal content voluntarily. - **Investing in Law Enforcement Capabilities**: Strengthening traditional investigative methods without compromising digital security. #### The technical community largely agrees that weakening encryption is not the solution: - **Consensus on Security**: Strong encryption is essential for the safety and privacy of all internet users. - **Call for Dialogue**: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights. --- ### **Global Reactions and the Debate in Europe** The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values. #### **Support for Chat Control** Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that: - **Enhanced Security**: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes. - **Responsibility of Service Providers**: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities. - **Public Safety Priorities**: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy. #### **Opposition within the EU** Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach. **Germany** - **Stance**: Germany has been one of the most vocal opponents of the proposed measures. - **Reasons**: - **Constitutional Concerns**: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications. - **Security Risks**: Weakening encryption is seen as a threat to cybersecurity. - **Legal Challenges**: Potential conflicts with national laws protecting personal data and communication secrecy. **Netherlands** - **Recent Developments**: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy. - **Arguments**: - **Effectiveness Doubts**: Skepticism about the actual effectiveness of the measures in combating crime. - **Negative Impact on Privacy**: Concerns about mass surveillance and the infringement of citizens' rights. Table reference: Patrick Breyer - Chat Control in 23 September 2024 #### **Privacy Advocacy Groups** **European Digital Rights (EDRi)** - **Role**: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment. - **Position**: - **Strong Opposition**: EDRi argues that Chat Control is incompatible with fundamental rights. - **Awareness Campaigns**: Engaging in public campaigns to inform citizens about the potential risks. - **Policy Engagement**: Lobbying policymakers to consider alternative approaches that respect privacy. **Politicians and Activists** **Patrick Breyer** - **Background**: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party. - **Actions**: - **Advocacy**: Actively campaigning against Chat Control through speeches, articles, and legislative efforts. - **Public Outreach**: Using social media and public events to raise awareness. - **Legal Expertise**: Highlighting the legal inconsistencies and potential violations of EU law. #### **Global Reactions** **International Organizations** - **Human Rights Watch and Amnesty International**: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider. **Technology Companies** - **Global Tech Firms**: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust. - **Industry Associations**: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness. <img src="https://blossom.primal.net/e761aa2dd240a1a2e7d943565ccbda427b5a8054bf4e6e17c946711ab6370d5d.png"> #### **The Broader Debate** The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include: - **Legal Precedents**: How the EU's decision might influence laws and regulations in other countries. - **Digital Sovereignty**: The desire of nations to control digital spaces within their borders. - **Civil Liberties**: The importance of protecting freedoms in the face of technological advancements. #### **Public Opinion** - **Diverse Views**: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all. - **Awareness Levels**: Many people are still unaware of the potential changes, highlighting the need for public education on the issue. #### The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society. --- ### **Possible Consequences for Messaging Services** The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication. #### **Impact on Encrypted Messaging Services** **Signal and Similar Platforms** - **Compliance Challenges**: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles. - **Operational Decisions**: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features. #### **Potential Blocking or Limiting of Services** - **Regulatory Enforcement**: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU. - **Access Restrictions**: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements. #### **Effects on Smaller Providers** - **Resource Constraints**: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market. - **Innovation Stifling**: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector. <img src="https://blossom.primal.net/60a9cad69b45cc3ded1d1759312e49a57b3aa997db62e36016f40642943be5e9.png"> #### **User Experience and Trust** - **Privacy Concerns**: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement. - **Migration to Unregulated Platforms**: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks. #### **Technical and Security Implications** - **Increased Vulnerabilities**: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches. - **Global Security Risks**: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders. #### **Impact on Businesses and Professional Communications** - **Confidentiality Issues**: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services. - **Compliance Complexity**: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens. #### **Economic Consequences** - **Market Fragmentation**: Divergent regulations could lead to a fragmented market, with different versions of services for different regions. - **Loss of Revenue**: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance. #### **Responses from Service Providers** - **Legal Challenges**: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights. - **Policy Advocacy**: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control. #### **Possible Adaptations** - **Technological Innovation**: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain. - **Transparency Measures**: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy. #### The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape. --- ### **What Happens Next? The Future of Chat Control** The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union. #### **Current Status of Legislation** - **Ongoing Negotiations**: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders. - **Timeline**: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay. #### **Key Influencing Factors** **1. Legal Challenges and Compliance with EU Law** - **Fundamental Rights Assessment**: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression. - **Court Scrutiny**: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control. **2. Technological Feasibility** - **Development of Privacy-Preserving Technologies**: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies. - **Implementation Challenges**: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures. **3. Political Dynamics** - **Member State Positions**: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations. - **Public Opinion and Advocacy**: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections. **4. Industry Responses** - **Negotiations with Service Providers**: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed. - **Potential for Self-Regulation**: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning. #### **Possible Scenarios** **Optimistic Outcome:** - **Balanced Regulation**: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight. **Pessimistic Outcome:** - **Adoption of Strict Measures**: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market. **Middle Ground:** - **Incremental Implementation**: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact. #### **How to Stay Informed and Protect Your Privacy** - **Follow Reputable Sources**: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments. - **Engage in the Dialogue**: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy. - **Utilize Secure Practices**: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security. <img src="https://blossom.primal.net/1e2c0cd70d88629c54ac84f928ab107f08f698d2c7f0df511277fb44c1480f0a.png"> #### **The Global Perspective** - **International Implications**: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against. - **Collaboration Opportunities**: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats. #### **Looking Ahead** The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders. As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world. --- ### **Conclusion** The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns. Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits. The potential consequences of implementing Chat Control are far-reaching: - **Erosion of Trust**: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online. - **Security Vulnerabilities**: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks. - **Stifling Innovation**: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry. - **Global Implications**: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse. As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values. The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free. In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world. <img src="https://blossom.primal.net/d3f07d8bc7a49ac291f14eb449879462c76ae407abbe728ddc6f93e11fabe11d.png"> --- Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future. ## Read more: - https://www.patrick-breyer.de/en/posts/chat-control/ - https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/ - https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/ - https://signal.org/blog/pdfs/ndss-keynote.pdf - https://tuta.com/blog/germany-stop-chat-control - https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal - https://mullvad.net/en/why-privacy-matters @ fd208ee8:0fd927c1
2024-10-20 18:19:48(Please note that this is not official financial or business advice, but rather a description of something we have done, on an informal basis.) # A long, long time ago It's been nearly a year, since nostr:nprofile1qydhwumn8ghj7argv4nx7un9wd6zumn0wd68yvfwvdhk6tcpypmhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjj7qpqs3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqv5atj2 came into being, mostly as a lark, involving a couple of members of our private chat group. Our initial plan was to work toward bounties, but Nostr bounties are a bit of a biased, uncertain thing, and our enthusiasm for that quickly waned. So, what to do? Here we are, we three (nostr:npub1ecdlntvjzexlyfale2egzvvncc8tgqsaxkl5hw7xlgjv2cxs705s9qs735, nostr:npub1wqfzz2p880wq0tumuae9lfwyhs8uz35xd0kr34zrvrwyh3kvrzuskcqsyn, and I): IT professionals with little time, but plenty of intellectual energy, a Slack chat, a [GitHub repo](https://github.com/ShadowySupercode), and lots of frustration with the Nostr status quo. We were, you see, Nostr end-users. We loved the idea of the protocol, but we were being regularly stymied by the poor quality of many implementations. * Why can I not login? Oh, they fixed the login! Nope, still can't login. * If I press this button, it says it sent, but it didn't send. Where note? * They announced a new feature, but I tried it and it didn't work. Oh well. * I noticed a bug in the client, reported it, and the issue is just rotting away in the project repo. Ignored. * The website/relay/repo was here... yesterday. Today it has disappeared, and taken my zaps with it. It was enough to make us want to tear our hair out. We decided that what Nostr needed... what it _really_ needed... was a **Nostr Stable Version**. Nothing glamorous. Nothing exotic. Nothing busy or excitable. Just something that stayed where you initially found it, ran, and actually worked. Something where you could report a bug and receive a prompt response. Maybe even something, where you could pay a reasonable fee and be _allowed to have expectations_ of some particular service being returned. And who better to build such a version, than people who want to use it, themselves? # Things working is an underrated concept I know that the very idea of software _running as expected_ and websites not appearing and disappearing suddenly, based upon what some particular developer had for lunch, tends to be met with little but scorn, from hardened, seasoned Nostriches (who are convinced that bugs are _all_ features), but I think the majority of potential users would see it differently. I'm with the majority, on this one. I like to click "save" buttons and have them save. If I publish something, I want it to appear under my list of published somethings. I like to type in the website address I always type in, and have it magically appear on my screen, as if there were a little man sitting at controls in my laptop, just waiting for me to write H-T-T-P-S... and then jump to attention. My unreasonable expectations have no bounds, it is true. But unreasonable people are also people, so we would also like to have our own unreasonable things to play with. Scorn away. My save button will save, and my published something will publish, and my website will load _every damn time_, just to spite you. In the larger scheme of things, you see, we win even if we fail, if we at least increase the competition enough, that _things working_ becomes the new standard. We can simply prove, definitively, that it is possible for Nostr things to work, if they are built by people who care if they work. If we also have fun together, learn something new, and come up with some cool, novel use cases, then that's pure profit. We can only win, at this endeavor. # Where to start? ## Name that brand So, we had a team, we had a business idea, and we had a heck of a lot of motivation. What we didn't have, is a name. (Never underestimate the importance of naming things.) We decided to name ourselves "GitCitadel" because "git" sounds techy, hints at our GitRepublic project, and is reminiscent of open-source development, and "citadel" reminds us of Bitcoin. The republic is at home in the citadel, naturally. All other products also live in the same citadel, hence the naming-convention of prefacing everything with "GC" (i.e. "GC Alexandria", "GC Sybil", "GC Aedile", etc.). ## Brand yourself The next thing we did, was rent a domain and run a webserver on it. This is an important step because it gives you an Internet presence, allows you to have company NIP-05 and email addresses (a form of promotion), and it's simply exciting to have one. Feels so much more "official" and it helps increase the name-recognition of your company. ## Define yourself We then sat down, together, over the Internet, and figured out who we are. Not who we individually are, but who we are, as a company. A company, after all, (according to the Cambridge Dictionary) is "an organization that produces or sells goods or services in order to make a profit". Now, a company's profits don't have to be monetary, but they should be something tangible. A company, in other words, is a team of people working toward some defined goal. What is our goal? Well, we decided to think it over, sat down with the newer additions to the company (you can see who they are, on our [project wiki page](https://wikistr.com/gitcitadel-project), and came up with a Vision and a Mission:  The _vision_ is what the overall goals of the company are, whereas the _mission_ describes how those goals shall be achieved. Now, this is a sort of lofty, abstract statement, so it was important that we posted it someplace publicly (to keep ourselves accountable) and look at it regularly, so that we can ponder it and realign whatever we are currently working on, with this statement. We know the statement is well-designed, if considering it helps us make decisions about what to do next. ## Pay yourselves (I'm going to switch from "we" to "you", here, as it's easier to write this part, but let's just pretend I didn't.)  The next thing on the list, is to arrange the finances, usually by setting up a Geyserfund, with an associated wallet, and then deciding how the funds from the wallet will be dispersed or stored. (I won't tell you how we are handling that, as that's internal company business, but I'm sure you'll think of something clever, yourselves. Or just google it.) I would encourage you to arrange to pay yourselves profits. Not merely because your idea is going to make you all fabulously wealthy and internationally famous (although, that is obviously true), but because _profits are the most pure form of communication that consumers in the market have_ with its producers, and one of the best ways to make decisions and measure increases in efficiency (increasing profits and/or output, while keeping prices steady or falling). Cutting off this signal, in order to look pious to outsiders, is to shoot yourself in your free-market foot. Nobody says that you have to spend your profits on the proverbial _lambo and a bimbo_. You could donate them to charity, reinvest them, or store them for your nephews to inherit, but **pay them out, you should**. You don't have to love money, to value it as a tool and use it shrewdly. Money is a measure, and companies should regularly measure themselves: against their previous state, against their potential state, and against their competition. (Also, you can use money to buy a lambo and a bimbo, but you didn't hear that from me.) ## Organize yourselves Once you've been working together, for a while, you'll find that you need to figure out how to organize yourselves. The first step is to... ### Form a board of directors. Stop laughing. I'm serious. Any company has at least two roles (President and Secretary), ideally held by two different people, so any single-proprietor company is a man down. Find a different person, to be your Second, even if they're just your confident, who lets you cry on your shoulder on The Bad Days, when your code refuses to compile, and can tell people that you've become a Bitcoin millionaire and have gone on a sabbatical to hike the Himalayas and will be back in 3 months on The Very Good Days. Because business man was not meant to be alone. If, like us, you're a small herd of people and have already been working together for a while, then this step is actually really, really fun. Just think about what people are already doing, and put a label on it. That role is now defined and it is clear who is in charge of what. Scientists become "Chief Science Officer" or "Scientific Advisor". The person who always writes the _okay, so this is what we've decided_ comment in the thread becomes the Secretary, the one managing the Lightning wallet and worrying over paying for the servers is the CFO, the person running the remote server becomes the CTO, and so on and etc. And everyone knows who the CEO is. Everyone always knows. They do. Just write it down. ### Agree how to disagree Now, have the secretary write up a Member's Agreement. It's a contract between the members, about whatever the group thinks is important concerning the way the company will operate. According to [Investopedia](https://www.investopedia.com/terms/l/llc-operating-agreement.asp), common topics are:  Is this legally binding? Probably not. Maybe. I don't know and wouldn't tell you, even if I did. But it's _emotionally binding_, which is arguably more important. Writing things down is an advanced form of _naming things_ and it provides clarity, helps to manage expectations, and allows you to define a working agreement before Real Money shows up and taints your interaction. You're just accepting tips, at the moment. Everyone is calm and cheerful, so now is your best time to negotiate. Keep it very simple and only address the most basic things. If you wish to incorporate, at a later date, then you just take this to a registered agent, or other experienced person, and have them tidy up any loose ends and add the fine print. ## Go forth, together This has probably taken you weeks, or even months, but you're now a company. Get a logo and a company npub, start dropping the company name into your notes, and get on with the business of being in business.
@ fd208ee8:0fd927c1
2024-10-20 18:19:48(Please note that this is not official financial or business advice, but rather a description of something we have done, on an informal basis.) # A long, long time ago It's been nearly a year, since nostr:nprofile1qydhwumn8ghj7argv4nx7un9wd6zumn0wd68yvfwvdhk6tcpypmhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjj7qpqs3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqv5atj2 came into being, mostly as a lark, involving a couple of members of our private chat group. Our initial plan was to work toward bounties, but Nostr bounties are a bit of a biased, uncertain thing, and our enthusiasm for that quickly waned. So, what to do? Here we are, we three (nostr:npub1ecdlntvjzexlyfale2egzvvncc8tgqsaxkl5hw7xlgjv2cxs705s9qs735, nostr:npub1wqfzz2p880wq0tumuae9lfwyhs8uz35xd0kr34zrvrwyh3kvrzuskcqsyn, and I): IT professionals with little time, but plenty of intellectual energy, a Slack chat, a [GitHub repo](https://github.com/ShadowySupercode), and lots of frustration with the Nostr status quo. We were, you see, Nostr end-users. We loved the idea of the protocol, but we were being regularly stymied by the poor quality of many implementations. * Why can I not login? Oh, they fixed the login! Nope, still can't login. * If I press this button, it says it sent, but it didn't send. Where note? * They announced a new feature, but I tried it and it didn't work. Oh well. * I noticed a bug in the client, reported it, and the issue is just rotting away in the project repo. Ignored. * The website/relay/repo was here... yesterday. Today it has disappeared, and taken my zaps with it. It was enough to make us want to tear our hair out. We decided that what Nostr needed... what it _really_ needed... was a **Nostr Stable Version**. Nothing glamorous. Nothing exotic. Nothing busy or excitable. Just something that stayed where you initially found it, ran, and actually worked. Something where you could report a bug and receive a prompt response. Maybe even something, where you could pay a reasonable fee and be _allowed to have expectations_ of some particular service being returned. And who better to build such a version, than people who want to use it, themselves? # Things working is an underrated concept I know that the very idea of software _running as expected_ and websites not appearing and disappearing suddenly, based upon what some particular developer had for lunch, tends to be met with little but scorn, from hardened, seasoned Nostriches (who are convinced that bugs are _all_ features), but I think the majority of potential users would see it differently. I'm with the majority, on this one. I like to click "save" buttons and have them save. If I publish something, I want it to appear under my list of published somethings. I like to type in the website address I always type in, and have it magically appear on my screen, as if there were a little man sitting at controls in my laptop, just waiting for me to write H-T-T-P-S... and then jump to attention. My unreasonable expectations have no bounds, it is true. But unreasonable people are also people, so we would also like to have our own unreasonable things to play with. Scorn away. My save button will save, and my published something will publish, and my website will load _every damn time_, just to spite you. In the larger scheme of things, you see, we win even if we fail, if we at least increase the competition enough, that _things working_ becomes the new standard. We can simply prove, definitively, that it is possible for Nostr things to work, if they are built by people who care if they work. If we also have fun together, learn something new, and come up with some cool, novel use cases, then that's pure profit. We can only win, at this endeavor. # Where to start? ## Name that brand So, we had a team, we had a business idea, and we had a heck of a lot of motivation. What we didn't have, is a name. (Never underestimate the importance of naming things.) We decided to name ourselves "GitCitadel" because "git" sounds techy, hints at our GitRepublic project, and is reminiscent of open-source development, and "citadel" reminds us of Bitcoin. The republic is at home in the citadel, naturally. All other products also live in the same citadel, hence the naming-convention of prefacing everything with "GC" (i.e. "GC Alexandria", "GC Sybil", "GC Aedile", etc.). ## Brand yourself The next thing we did, was rent a domain and run a webserver on it. This is an important step because it gives you an Internet presence, allows you to have company NIP-05 and email addresses (a form of promotion), and it's simply exciting to have one. Feels so much more "official" and it helps increase the name-recognition of your company. ## Define yourself We then sat down, together, over the Internet, and figured out who we are. Not who we individually are, but who we are, as a company. A company, after all, (according to the Cambridge Dictionary) is "an organization that produces or sells goods or services in order to make a profit". Now, a company's profits don't have to be monetary, but they should be something tangible. A company, in other words, is a team of people working toward some defined goal. What is our goal? Well, we decided to think it over, sat down with the newer additions to the company (you can see who they are, on our [project wiki page](https://wikistr.com/gitcitadel-project), and came up with a Vision and a Mission:  The _vision_ is what the overall goals of the company are, whereas the _mission_ describes how those goals shall be achieved. Now, this is a sort of lofty, abstract statement, so it was important that we posted it someplace publicly (to keep ourselves accountable) and look at it regularly, so that we can ponder it and realign whatever we are currently working on, with this statement. We know the statement is well-designed, if considering it helps us make decisions about what to do next. ## Pay yourselves (I'm going to switch from "we" to "you", here, as it's easier to write this part, but let's just pretend I didn't.)  The next thing on the list, is to arrange the finances, usually by setting up a Geyserfund, with an associated wallet, and then deciding how the funds from the wallet will be dispersed or stored. (I won't tell you how we are handling that, as that's internal company business, but I'm sure you'll think of something clever, yourselves. Or just google it.) I would encourage you to arrange to pay yourselves profits. Not merely because your idea is going to make you all fabulously wealthy and internationally famous (although, that is obviously true), but because _profits are the most pure form of communication that consumers in the market have_ with its producers, and one of the best ways to make decisions and measure increases in efficiency (increasing profits and/or output, while keeping prices steady or falling). Cutting off this signal, in order to look pious to outsiders, is to shoot yourself in your free-market foot. Nobody says that you have to spend your profits on the proverbial _lambo and a bimbo_. You could donate them to charity, reinvest them, or store them for your nephews to inherit, but **pay them out, you should**. You don't have to love money, to value it as a tool and use it shrewdly. Money is a measure, and companies should regularly measure themselves: against their previous state, against their potential state, and against their competition. (Also, you can use money to buy a lambo and a bimbo, but you didn't hear that from me.) ## Organize yourselves Once you've been working together, for a while, you'll find that you need to figure out how to organize yourselves. The first step is to... ### Form a board of directors. Stop laughing. I'm serious. Any company has at least two roles (President and Secretary), ideally held by two different people, so any single-proprietor company is a man down. Find a different person, to be your Second, even if they're just your confident, who lets you cry on your shoulder on The Bad Days, when your code refuses to compile, and can tell people that you've become a Bitcoin millionaire and have gone on a sabbatical to hike the Himalayas and will be back in 3 months on The Very Good Days. Because business man was not meant to be alone. If, like us, you're a small herd of people and have already been working together for a while, then this step is actually really, really fun. Just think about what people are already doing, and put a label on it. That role is now defined and it is clear who is in charge of what. Scientists become "Chief Science Officer" or "Scientific Advisor". The person who always writes the _okay, so this is what we've decided_ comment in the thread becomes the Secretary, the one managing the Lightning wallet and worrying over paying for the servers is the CFO, the person running the remote server becomes the CTO, and so on and etc. And everyone knows who the CEO is. Everyone always knows. They do. Just write it down. ### Agree how to disagree Now, have the secretary write up a Member's Agreement. It's a contract between the members, about whatever the group thinks is important concerning the way the company will operate. According to [Investopedia](https://www.investopedia.com/terms/l/llc-operating-agreement.asp), common topics are:  Is this legally binding? Probably not. Maybe. I don't know and wouldn't tell you, even if I did. But it's _emotionally binding_, which is arguably more important. Writing things down is an advanced form of _naming things_ and it provides clarity, helps to manage expectations, and allows you to define a working agreement before Real Money shows up and taints your interaction. You're just accepting tips, at the moment. Everyone is calm and cheerful, so now is your best time to negotiate. Keep it very simple and only address the most basic things. If you wish to incorporate, at a later date, then you just take this to a registered agent, or other experienced person, and have them tidy up any loose ends and add the fine print. ## Go forth, together This has probably taken you weeks, or even months, but you're now a company. Get a logo and a company npub, start dropping the company name into your notes, and get on with the business of being in business. @ b6ca2216:f45f8b5b
2024-10-20 00:19:37my 3. article
@ b6ca2216:f45f8b5b
2024-10-20 00:19:37my 3. article @ b6ca2216:f45f8b5b
2024-10-20 00:16:38{"id":12345,"title":"deleted","body":"deleted"}
@ b6ca2216:f45f8b5b
2024-10-20 00:16:38{"id":12345,"title":"deleted","body":"deleted"} @ b6ca2216:f45f8b5b
2024-10-19 23:51:01{id:123, title:"my first article", body:"This NIP defines kind:30402: an addressable event to describe classified listings that list any arbitrary product, service, or other thing for sale or offer and includes enough structured metadata to make them useful. The category of classifieds includes a very broad range of physical goods, services, work opportunities, rentals, free giveaways, personals, etc. and is distinct from the more strictly structured marketplaces defined in NIP-15 that often sell many units of specific products through very specific channels. The structure of these events is very similar to NIP-23 long-form content events."}
@ b6ca2216:f45f8b5b
2024-10-19 23:51:01{id:123, title:"my first article", body:"This NIP defines kind:30402: an addressable event to describe classified listings that list any arbitrary product, service, or other thing for sale or offer and includes enough structured metadata to make them useful. The category of classifieds includes a very broad range of physical goods, services, work opportunities, rentals, free giveaways, personals, etc. and is distinct from the more strictly structured marketplaces defined in NIP-15 that often sell many units of specific products through very specific channels. The structure of these events is very similar to NIP-23 long-form content events."} @ a95c6243:d345522c
2024-10-19 08:58:08Ein Lämmchen löschte an einem Bache seinen Durst. Fern von ihm, aber näher der Quelle, tat ein Wolf das gleiche. Kaum erblickte er das Lämmchen, so schrie er: "Warum trübst du mir das Wasser, das ich trinken will?" "Wie wäre das möglich", erwiderte schüchtern das Lämmchen, "ich stehe hier unten und du so weit oben; das Wasser fließt ja von dir zu mir; glaube mir, es kam mir nie in den Sinn, dir etwas Böses zu tun!" "Ei, sieh doch! Du machst es gerade, wie dein Vater vor sechs Monaten; ich erinnere mich noch sehr wohl, daß auch du dabei warst, aber glücklich entkamst, als ich ihm für sein Schmähen das Fell abzog!" "Ach, Herr!" flehte das zitternde Lämmchen, "ich bin ja erst vier Wochen alt und kannte meinen Vater gar nicht, so lange ist er schon tot; wie soll ich denn für ihn büßen." "Du Unverschämter!" so endigt der Wolf mit erheuchelter Wut, indem er die Zähne fletschte. "Tot oder nicht tot, weiß ich doch, daß euer ganzes Geschlecht mich hasset, und dafür muß ich mich rächen." Ohne weitere Umstände zu machen, zerriß er das Lämmchen und verschlang es. *Das [Gewissen](https://apollo-news.net/das-gewissen-in-corona-jahren-zum-tod-von-gunnar-kaiser/) regt sich selbst bei dem größten Bösewichte; er sucht doch nach Vorwand, um dasselbe damit bei Begehung seiner Schlechtigkeiten zu beschwichtigen.* Quelle: https://eden.one/fabeln-aesop-das-lamm-und-der-wolf
@ a95c6243:d345522c
2024-10-19 08:58:08Ein Lämmchen löschte an einem Bache seinen Durst. Fern von ihm, aber näher der Quelle, tat ein Wolf das gleiche. Kaum erblickte er das Lämmchen, so schrie er: "Warum trübst du mir das Wasser, das ich trinken will?" "Wie wäre das möglich", erwiderte schüchtern das Lämmchen, "ich stehe hier unten und du so weit oben; das Wasser fließt ja von dir zu mir; glaube mir, es kam mir nie in den Sinn, dir etwas Böses zu tun!" "Ei, sieh doch! Du machst es gerade, wie dein Vater vor sechs Monaten; ich erinnere mich noch sehr wohl, daß auch du dabei warst, aber glücklich entkamst, als ich ihm für sein Schmähen das Fell abzog!" "Ach, Herr!" flehte das zitternde Lämmchen, "ich bin ja erst vier Wochen alt und kannte meinen Vater gar nicht, so lange ist er schon tot; wie soll ich denn für ihn büßen." "Du Unverschämter!" so endigt der Wolf mit erheuchelter Wut, indem er die Zähne fletschte. "Tot oder nicht tot, weiß ich doch, daß euer ganzes Geschlecht mich hasset, und dafür muß ich mich rächen." Ohne weitere Umstände zu machen, zerriß er das Lämmchen und verschlang es. *Das [Gewissen](https://apollo-news.net/das-gewissen-in-corona-jahren-zum-tod-von-gunnar-kaiser/) regt sich selbst bei dem größten Bösewichte; er sucht doch nach Vorwand, um dasselbe damit bei Begehung seiner Schlechtigkeiten zu beschwichtigen.* Quelle: https://eden.one/fabeln-aesop-das-lamm-und-der-wolf @ 8947a945:9bfcf626
2024-10-17 08:06:55[](https://stock.adobe.com/stock-photo/id/1010191703) **สวัสดีทุกคนบน Nostr ครับ** รวมไปถึง **watchers**และ **ผู้ติดตาม**ของผมจาก Deviantart และ platform งานศิลปะอื่นๆนะครับ ตั้งแต่ต้นปี 2024 ผมใช้ AI เจนรูปงานตัวละครสาวๆจากอนิเมะ และเปิด exclusive content ให้สำหรับผู้ที่ชื่นชอบผลงานของผมเป็นพิเศษ ผมโพสผลงานผมทั้งหมดไว้ที่เวบ Deviantart และค่อยๆสร้างฐานผู้ติดตามมาเรื่อยๆอย่างค่อยเป็นค่อยไปมาตลอดครับ ทุกอย่างเติบโตไปเรื่อยๆของมัน ส่วนตัวผมมองว่ามันเป็นพิร์ตธุรกิจออนไลน์ ของผมพอร์ตนึงได้เลย **เมื่อวันที่ 16 กย.2024** มีผู้ติดตามคนหนึ่งส่งข้อความส่วนตัวมาหาผม บอกว่าชื่นชอบผลงานของผมมาก ต้องการจะขอซื้อผลงาน แต่ขอซื้อเป็น NFT นะ เสนอราคาซื้อขายต่อชิ้นที่สูงมาก หลังจากนั้นผมกับผู้ซื้อคนนี้พูดคุยกันในเมล์ครับ  ### นี่คือข้อสรุปสั่นๆจากการต่อรองซื้อขายครับ (หลังจากนี้ผมขอเรียกผู้ซื้อว่า scammer นะครับ เพราะไพ่มันหงายมาแล้ว ว่าเขาคือมิจฉาชีพ)  - Scammer รายแรก เลือกผลงานที่จะซื้อ เสนอราคาซื้อที่สูงมาก แต่ต้องเป็นเวบไซต์ NFTmarket place ที่เขากำหนดเท่านั้น มันทำงานอยู่บน ERC20 ผมเข้าไปดูเวบไซต์ที่ว่านี้แล้วรู้สึกว่ามันดูแปลกๆครับ คนที่จะลงขายผลงานจะต้องใช้ email ในการสมัครบัญชีซะก่อน ถึงจะผูก wallet อย่างเช่น metamask ได้ เมื่อผูก wallet แล้วไม่สามารถเปลี่ยนได้ด้วย ตอนนั้นผมใช้ wallet ที่ไม่ได้ link กับ HW wallet ไว้ ทดลองสลับ wallet ไปๆมาๆ มันทำไม่ได้ แถมลอง log out แล้ว เลข wallet ก็ยังคาอยู่อันเดิม อันนี้มันดูแปลกๆแล้วหนึ่งอย่าง เวบนี้ค่า ETH ในการ mint **0.15 - 0.2 ETH** … ตีเป็นเงินบาทนี่แพงบรรลัยอยู่นะครับ  - Scammer รายแรกพยายามชักจูงผม หว่านล้อมผมว่า แหม เดี๋ยวเขาก็มารับซื้องานผมน่า mint งานเสร็จ รีบบอกเขานะ เดี๋ยวเขารีบกดซื้อเลย พอขายได้กำไร ผมก็ได้ค่า gas คืนได้ แถมยังได้กำไรอีก ไม่มีอะไรต้องเสีนจริงมั้ย แต่มันเป้นความโชคดีครับ เพราะตอนนั้นผมไม่เหลือทุนสำรองที่จะมาซื้อ ETH ได้ ผมเลยต่อรองกับเขาตามนี้ครับ : 1. ผมเสนอว่า เอางี้มั้ย ผมส่งผลงานของผมแบบ low resolution ให้ก่อน แลกกับให้เขาช่วยโอน ETH ที่เป็นค่า mint งานมาให้หน่อย พอผมได้ ETH แล้ว ผมจะ upscale งานของผม แล้วเมล์ไปให้ ใจแลกใจกันไปเลย ... เขาไม่เอา 2. ผมเสนอให้ไปซื้อที่ร้านค้าออนไลน์ buymeacoffee ของผมมั้ย จ่ายเป็น USD ... เขาไม่เอา 3. ผมเสนอให้ซื้อขายผ่าน PPV lightning invoice ที่ผมมีสิทธิ์เข้าถึง เพราะเป็น creator ของ Creatr ... เขาไม่เอา 4. ผมยอกเขาว่างั้นก็รอนะ รอเงินเดือนออก เขาบอก ok สัปดาห์ถัดมา มี scammer คนที่สองติดต่อผมเข้ามา ใช้วิธีการใกล้เคียงกัน แต่ใช้คนละเวบ แถมเสนอราคาซื้อที่สูงกว่าคนแรกมาก เวบที่สองนี้เลวร้ายค่าเวบแรกอีกครับ คือต้องใช้เมล์สมัครบัญชี ไม่สามารถผูก metamask ได้ พอสมัครเสร็จจะได้ wallet เปล่าๆมาหนึ่งอัน ผมต้องโอน ETH เข้าไปใน wallet นั้นก่อน เพื่อเอาไปเป็นค่า mint NFT **0.2 ETH** ผมบอก scammer รายที่สองว่า ต้องรอนะ เพราะตอนนี้กำลังติดต่อซื้อขายอยู่กับผู้ซื้อรายแรกอยู่ ผมกำลังรอเงินเพื่อมาซื้อ ETH เป็นต้นทุนดำเนินงานอยู่ คนคนนี้ขอให้ผมส่งเวบแรกไปให้เขาดูหน่อย หลังจากนั้นไม่นานเขาเตือนผมมาว่าเวบแรกมันคือ scam นะ ไม่สามารถถอนเงินออกมาได้ เขายังส่งรูป cap หน้าจอที่คุยกับผู้เสียหายจากเวบแรกมาให้ดูว่าเจอปัญหาถอนเงินไม่ได้ ไม่พอ เขายังบลัฟ opensea ด้วยว่าลูกค้าขายงานได้ แต่ถอนเงินไม่ได้ **Opensea ถอนเงินไม่ได้ ตรงนี้แหละครับคือตัวกระตุกต่อมเอ๊ะของผมดังมาก** เพราะ opensea อ่ะ ผู้ใช้ connect wallet เข้ากับ marketplace โดยตรง ซื้อขายกันเกิดขึ้น เงินวิ่งเข้าวิ่งออก wallet ของแต่ละคนโดยตรงเลย opensea เก็บแค่ค่า fee ในการใช้ platform ไม่เก็บเงินลูกค้าไว้ แถมปีนี้ค่า gas fee ก็ถูกกว่า bull run cycle 2020 มาก ตอนนี้ค่า gas fee ประมาณ 0.0001 ETH (แต่มันก็แพงกว่า BTC อยู่ดีอ่ะครับ) ผมเลยเอาเรื่องนี้ไปปรึกษาพี่บิท แต่แอดมินมาคุยกับผมแทน ทางแอดมินแจ้งว่ายังไม่เคยมีเพื่อนๆมาปรึกษาเรื่องนี้ กรณีที่ผมทักมาถามนี่เป็นรายแรกเลย แต่แอดมินให้ความเห็นไปในทางเดียวกับสมมุติฐานของผมว่าน่าจะ scam ในเวลาเดียวกับผมเอาเรื่องนี้ไปถามในเพจ NFT community คนไทนด้วย ได้รับการ confirm ชัดเจนว่า scam และมีคนไม่น้อยโดนหลอก หลังจากที่ผมรู้ที่มาแล้ว ผมเลยเล่นสงครามปั่นประสาท scammer ทั้งสองคนนี้ครับ เพื่อดูว่าหลอกหลวงมิจฉาชีพจริงมั้ย โดยวันที่ 30 กย. ผมเลยปั่นประสาน scammer ทั้งสองรายนี้ โดยการ mint ผลงานที่เขาเสนอซื้อนั่นแหละ ขึ้น opensea แล้วส่งข้อความไปบอกว่า mint ให้แล้วนะ แต่เงินไม่พอจริงๆว่ะโทษที เลย mint ขึ้น opensea แทน พอดีบ้านจน ทำได้แค่นี้ไปถึงแค่ opensea รีบไปซื้อล่ะ มีคนจ้องจะคว้างานผมเยอะอยู่ ผมไม่คิด royalty fee ด้วยนะเฮ้ย เอาไปขายต่อไม่ต้องแบ่งกำไรกับผม เท่านั้นแหละครับ สงครามจิตวิทยาก็เริ่มขึ้น แต่เขาจนมุม กลืนน้ำลายตัวเอง ช็อตเด็ดคือ เขา : เนี่ยอุส่ารอ บอกเพื่อนในทีมว่าวันจันทร์ที่ 30 กย. ได้ของแน่ๆ เพื่อนๆในทีมเห็นงานผมแล้วมันสวยจริง เลยใส่เงินเต็มที่ 9.3ETH (+ capture screen ส่งตัวเลขยอดเงินมาให้ดู)ไว้รอโดยเฉพาะเลยนะ ผม : เหรอ ... งั้น ขอดู wallet address ที่มี transaction มาให้ดูหน่อยสิ เขา : 2ETH นี่มัน 5000$ เลยนะ ผม : แล้วไง ขอดู wallet address ที่มีการเอายอดเงิน 9.3ETH มาให้ดูหน่อย ไหนบอกว่าเตรียมเงินไว้มากแล้วนี่ ขอดูหน่อย ว่าใส่ไว้เมื่อไหร่ ... เอามาแค่ adrress นะเว้ย ไม่ต้องทะลึ่งส่ง seed มาให้ เขา : ส่งรูปเดิม 9.3 ETH มาให้ดู ผม : รูป screenshot อ่ะ มันไม่มีความหมายหรอกเว้ย ตัดต่อเอาก็ได้ง่ายจะตาย เอา transaction hash มาดู ไหนว่าเตรียมเงินไว้รอ 9.3ETH แล้วอยากซื้องานผมจนตัวสั่นเลยไม่ใช่เหรอ ถ้าจะส่ง wallet address มาให้ดู หรือจะช่วยส่ง 0.15ETH มาให้ยืม mint งานก่อน แล้วมากดซื้อ 2ETH ไป แล้วผมใช้ 0.15ETH คืนให้ก็ได้ จะซื้อหรือไม่ซื้อเนี่ย เขา : จะเอา address เขาไปทำไม ผม : ตัดจบ รำคาญ ไม่ขายให้ละ เขา : 2ETH = 5000 USD เลยนะ ผม : แล้วไง ผมเลยเขียนบทความนี้มาเตือนเพื่อนๆพี่ๆทุกคนครับ เผื่อใครกำลังเปิดพอร์ตทำธุรกิจขาย digital art online แล้วจะโชคดี เจอของดีแบบผม ----------- ### ทำไมผมถึงมั่นใจว่ามันคือการหลอกหลวง แล้วคนโกงจะได้อะไร [](https://stock.adobe.com/stock-photo/id/1010196295) อันดับแรกไปพิจารณาดู opensea ครับ เป็นเวบ NFTmarketplace ที่ volume การซื้อขายสูงที่สุด เขาไม่เก็บเงินของคนจะซื้อจะขายกันไว้กับตัวเอง เงินวิ่งเข้าวิ่งออก wallet ผู้ซื้อผู้ขายเลย ส่วนทางเวบเก็บค่าธรรมเนียมเท่านั้น แถมค่าธรรมเนียมก็ถูกกว่าเมื่อปี 2020 เยอะ ดังนั้นการที่จะไปลงขายงานบนเวบ NFT อื่นที่ค่า fee สูงกว่ากันเป็นร้อยเท่า ... จะทำไปทำไม ผมเชื่อว่า scammer โกงเงินเจ้าของผลงานโดยการเล่นกับความโลภและความอ่อนประสบการณ์ของเจ้าของผลงานครับ เมื่อไหร่ก็ตามที่เจ้าของผลงานโอน ETH เข้าไปใน wallet เวบนั้นเมื่อไหร่ หรือเมื่อไหร่ก็ตามที่จ่ายค่า fee ในการ mint งาน เงินเหล่านั้นสิ่งเข้ากระเป๋า scammer ทันที แล้วก็จะมีการเล่นตุกติกต่อแน่นอนครับ เช่นถอนไม่ได้ หรือซื้อไม่ได้ ต้องโอนเงินมาเพิ่มเพื่อปลดล็อค smart contract อะไรก็ว่าไป แล้วคนนิสัยไม่ดีพวกเนี้ย ก็จะเล่นกับความโลภของคน เอาราคาเสนอซื้อที่สูงโคตรๆมาล่อ ... อันนี้ไม่ว่ากัน เพราะบนโลก NFT รูปภาพบางรูปที่ไม่ได้มีความเป็นศิลปะอะไรเลย มันดันขายกันได้ 100 - 150 ETH ศิลปินที่พยายามสร้างตัวก็อาจจะมองว่า ผลงานเรามีคนรับซื้อ 2 - 4 ETH ต่องานมันก็มากพอแล้ว (จริงๆมากเกินจนน่าตกใจด้วยซ้ำครับ) บนโลกของ BTC ไม่ต้องเชื่อใจกัน โอนเงินไปหากันได้ ปิดสมุดบัญชีได้โดยไม่ต้องเชื่อใจกัน บบโลกของ ETH **"code is law"** smart contract มีเขียนอยู่แล้ว ไปอ่าน มันไม่ได้ยากมากในการทำความเข้าใจ ดังนั้น การจะมาเชื่อคำสัญญาจากคนด้วยกัน เป็นอะไรที่ไม่มีเหตุผล ผมไปเล่าเรื่องเหล่านี้ให้กับ community งานศิลปะ ก็มีทั้งเสียงตอบรับที่ดี และไม่ดีปนกันไป มีบางคนยืนยันเสียงแข็งไปในทำนองว่า ไอ้เรื่องแบบเนี้ยไม่ได้กินเขาหรอก เพราะเขาตั้งใจแน่วแน่ว่างานศิลป์ของเขา เขาไม่เอาเข้ามายุ่งในโลก digital currency เด็ดขาด ซึ่งผมก็เคารพมุมมองเขาครับ แต่มันจะดีกว่ามั้ย ถ้าเราเปิดหูเปิดตาให้ทันเทคโนโลยี โดยเฉพาะเรื่อง digital currency , blockchain โดนโกงทีนึงนี่คือหมดตัวกันง่ายกว่าเงิน fiat อีก อยากจะมาเล่าให้ฟังครับ และอยากให้ช่วยแชร์ไปให้คนรู้จักด้วย จะได้ระวังตัวกัน ## Note - ภาพประกอบ cyber security ทั้งสองนี่ของผมเองครับ ทำเอง วางขายบน AdobeStock - อีกบัญชีนึงของผม "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw กำลังค่อยๆเอาผลงานจากโลกข้างนอกเข้ามา nostr ครับ ตั้งใจจะมาสร้างงานศิลปะในนี้ เพื่อนๆที่ชอบงาน จะได้ไม่ต้องออกไปหาที่ไหน ผลงานของผมครับ - Anime girl fanarts : [HikariHarmony](https://linktr.ee/hikariharmonypatreon) - [HikariHarmony on Nostr](https://shorturl.at/I8Nu4) - General art : [KeshikiRakuen](https://linktr.ee/keshikirakuen) - KeshikiRakuen อาจจะเป็นบัญชี nostr ที่สามของผม ถ้าไหวครับ
@ 8947a945:9bfcf626
2024-10-17 08:06:55[](https://stock.adobe.com/stock-photo/id/1010191703) **สวัสดีทุกคนบน Nostr ครับ** รวมไปถึง **watchers**และ **ผู้ติดตาม**ของผมจาก Deviantart และ platform งานศิลปะอื่นๆนะครับ ตั้งแต่ต้นปี 2024 ผมใช้ AI เจนรูปงานตัวละครสาวๆจากอนิเมะ และเปิด exclusive content ให้สำหรับผู้ที่ชื่นชอบผลงานของผมเป็นพิเศษ ผมโพสผลงานผมทั้งหมดไว้ที่เวบ Deviantart และค่อยๆสร้างฐานผู้ติดตามมาเรื่อยๆอย่างค่อยเป็นค่อยไปมาตลอดครับ ทุกอย่างเติบโตไปเรื่อยๆของมัน ส่วนตัวผมมองว่ามันเป็นพิร์ตธุรกิจออนไลน์ ของผมพอร์ตนึงได้เลย **เมื่อวันที่ 16 กย.2024** มีผู้ติดตามคนหนึ่งส่งข้อความส่วนตัวมาหาผม บอกว่าชื่นชอบผลงานของผมมาก ต้องการจะขอซื้อผลงาน แต่ขอซื้อเป็น NFT นะ เสนอราคาซื้อขายต่อชิ้นที่สูงมาก หลังจากนั้นผมกับผู้ซื้อคนนี้พูดคุยกันในเมล์ครับ  ### นี่คือข้อสรุปสั่นๆจากการต่อรองซื้อขายครับ (หลังจากนี้ผมขอเรียกผู้ซื้อว่า scammer นะครับ เพราะไพ่มันหงายมาแล้ว ว่าเขาคือมิจฉาชีพ)  - Scammer รายแรก เลือกผลงานที่จะซื้อ เสนอราคาซื้อที่สูงมาก แต่ต้องเป็นเวบไซต์ NFTmarket place ที่เขากำหนดเท่านั้น มันทำงานอยู่บน ERC20 ผมเข้าไปดูเวบไซต์ที่ว่านี้แล้วรู้สึกว่ามันดูแปลกๆครับ คนที่จะลงขายผลงานจะต้องใช้ email ในการสมัครบัญชีซะก่อน ถึงจะผูก wallet อย่างเช่น metamask ได้ เมื่อผูก wallet แล้วไม่สามารถเปลี่ยนได้ด้วย ตอนนั้นผมใช้ wallet ที่ไม่ได้ link กับ HW wallet ไว้ ทดลองสลับ wallet ไปๆมาๆ มันทำไม่ได้ แถมลอง log out แล้ว เลข wallet ก็ยังคาอยู่อันเดิม อันนี้มันดูแปลกๆแล้วหนึ่งอย่าง เวบนี้ค่า ETH ในการ mint **0.15 - 0.2 ETH** … ตีเป็นเงินบาทนี่แพงบรรลัยอยู่นะครับ  - Scammer รายแรกพยายามชักจูงผม หว่านล้อมผมว่า แหม เดี๋ยวเขาก็มารับซื้องานผมน่า mint งานเสร็จ รีบบอกเขานะ เดี๋ยวเขารีบกดซื้อเลย พอขายได้กำไร ผมก็ได้ค่า gas คืนได้ แถมยังได้กำไรอีก ไม่มีอะไรต้องเสีนจริงมั้ย แต่มันเป้นความโชคดีครับ เพราะตอนนั้นผมไม่เหลือทุนสำรองที่จะมาซื้อ ETH ได้ ผมเลยต่อรองกับเขาตามนี้ครับ : 1. ผมเสนอว่า เอางี้มั้ย ผมส่งผลงานของผมแบบ low resolution ให้ก่อน แลกกับให้เขาช่วยโอน ETH ที่เป็นค่า mint งานมาให้หน่อย พอผมได้ ETH แล้ว ผมจะ upscale งานของผม แล้วเมล์ไปให้ ใจแลกใจกันไปเลย ... เขาไม่เอา 2. ผมเสนอให้ไปซื้อที่ร้านค้าออนไลน์ buymeacoffee ของผมมั้ย จ่ายเป็น USD ... เขาไม่เอา 3. ผมเสนอให้ซื้อขายผ่าน PPV lightning invoice ที่ผมมีสิทธิ์เข้าถึง เพราะเป็น creator ของ Creatr ... เขาไม่เอา 4. ผมยอกเขาว่างั้นก็รอนะ รอเงินเดือนออก เขาบอก ok สัปดาห์ถัดมา มี scammer คนที่สองติดต่อผมเข้ามา ใช้วิธีการใกล้เคียงกัน แต่ใช้คนละเวบ แถมเสนอราคาซื้อที่สูงกว่าคนแรกมาก เวบที่สองนี้เลวร้ายค่าเวบแรกอีกครับ คือต้องใช้เมล์สมัครบัญชี ไม่สามารถผูก metamask ได้ พอสมัครเสร็จจะได้ wallet เปล่าๆมาหนึ่งอัน ผมต้องโอน ETH เข้าไปใน wallet นั้นก่อน เพื่อเอาไปเป็นค่า mint NFT **0.2 ETH** ผมบอก scammer รายที่สองว่า ต้องรอนะ เพราะตอนนี้กำลังติดต่อซื้อขายอยู่กับผู้ซื้อรายแรกอยู่ ผมกำลังรอเงินเพื่อมาซื้อ ETH เป็นต้นทุนดำเนินงานอยู่ คนคนนี้ขอให้ผมส่งเวบแรกไปให้เขาดูหน่อย หลังจากนั้นไม่นานเขาเตือนผมมาว่าเวบแรกมันคือ scam นะ ไม่สามารถถอนเงินออกมาได้ เขายังส่งรูป cap หน้าจอที่คุยกับผู้เสียหายจากเวบแรกมาให้ดูว่าเจอปัญหาถอนเงินไม่ได้ ไม่พอ เขายังบลัฟ opensea ด้วยว่าลูกค้าขายงานได้ แต่ถอนเงินไม่ได้ **Opensea ถอนเงินไม่ได้ ตรงนี้แหละครับคือตัวกระตุกต่อมเอ๊ะของผมดังมาก** เพราะ opensea อ่ะ ผู้ใช้ connect wallet เข้ากับ marketplace โดยตรง ซื้อขายกันเกิดขึ้น เงินวิ่งเข้าวิ่งออก wallet ของแต่ละคนโดยตรงเลย opensea เก็บแค่ค่า fee ในการใช้ platform ไม่เก็บเงินลูกค้าไว้ แถมปีนี้ค่า gas fee ก็ถูกกว่า bull run cycle 2020 มาก ตอนนี้ค่า gas fee ประมาณ 0.0001 ETH (แต่มันก็แพงกว่า BTC อยู่ดีอ่ะครับ) ผมเลยเอาเรื่องนี้ไปปรึกษาพี่บิท แต่แอดมินมาคุยกับผมแทน ทางแอดมินแจ้งว่ายังไม่เคยมีเพื่อนๆมาปรึกษาเรื่องนี้ กรณีที่ผมทักมาถามนี่เป็นรายแรกเลย แต่แอดมินให้ความเห็นไปในทางเดียวกับสมมุติฐานของผมว่าน่าจะ scam ในเวลาเดียวกับผมเอาเรื่องนี้ไปถามในเพจ NFT community คนไทนด้วย ได้รับการ confirm ชัดเจนว่า scam และมีคนไม่น้อยโดนหลอก หลังจากที่ผมรู้ที่มาแล้ว ผมเลยเล่นสงครามปั่นประสาท scammer ทั้งสองคนนี้ครับ เพื่อดูว่าหลอกหลวงมิจฉาชีพจริงมั้ย โดยวันที่ 30 กย. ผมเลยปั่นประสาน scammer ทั้งสองรายนี้ โดยการ mint ผลงานที่เขาเสนอซื้อนั่นแหละ ขึ้น opensea แล้วส่งข้อความไปบอกว่า mint ให้แล้วนะ แต่เงินไม่พอจริงๆว่ะโทษที เลย mint ขึ้น opensea แทน พอดีบ้านจน ทำได้แค่นี้ไปถึงแค่ opensea รีบไปซื้อล่ะ มีคนจ้องจะคว้างานผมเยอะอยู่ ผมไม่คิด royalty fee ด้วยนะเฮ้ย เอาไปขายต่อไม่ต้องแบ่งกำไรกับผม เท่านั้นแหละครับ สงครามจิตวิทยาก็เริ่มขึ้น แต่เขาจนมุม กลืนน้ำลายตัวเอง ช็อตเด็ดคือ เขา : เนี่ยอุส่ารอ บอกเพื่อนในทีมว่าวันจันทร์ที่ 30 กย. ได้ของแน่ๆ เพื่อนๆในทีมเห็นงานผมแล้วมันสวยจริง เลยใส่เงินเต็มที่ 9.3ETH (+ capture screen ส่งตัวเลขยอดเงินมาให้ดู)ไว้รอโดยเฉพาะเลยนะ ผม : เหรอ ... งั้น ขอดู wallet address ที่มี transaction มาให้ดูหน่อยสิ เขา : 2ETH นี่มัน 5000$ เลยนะ ผม : แล้วไง ขอดู wallet address ที่มีการเอายอดเงิน 9.3ETH มาให้ดูหน่อย ไหนบอกว่าเตรียมเงินไว้มากแล้วนี่ ขอดูหน่อย ว่าใส่ไว้เมื่อไหร่ ... เอามาแค่ adrress นะเว้ย ไม่ต้องทะลึ่งส่ง seed มาให้ เขา : ส่งรูปเดิม 9.3 ETH มาให้ดู ผม : รูป screenshot อ่ะ มันไม่มีความหมายหรอกเว้ย ตัดต่อเอาก็ได้ง่ายจะตาย เอา transaction hash มาดู ไหนว่าเตรียมเงินไว้รอ 9.3ETH แล้วอยากซื้องานผมจนตัวสั่นเลยไม่ใช่เหรอ ถ้าจะส่ง wallet address มาให้ดู หรือจะช่วยส่ง 0.15ETH มาให้ยืม mint งานก่อน แล้วมากดซื้อ 2ETH ไป แล้วผมใช้ 0.15ETH คืนให้ก็ได้ จะซื้อหรือไม่ซื้อเนี่ย เขา : จะเอา address เขาไปทำไม ผม : ตัดจบ รำคาญ ไม่ขายให้ละ เขา : 2ETH = 5000 USD เลยนะ ผม : แล้วไง ผมเลยเขียนบทความนี้มาเตือนเพื่อนๆพี่ๆทุกคนครับ เผื่อใครกำลังเปิดพอร์ตทำธุรกิจขาย digital art online แล้วจะโชคดี เจอของดีแบบผม ----------- ### ทำไมผมถึงมั่นใจว่ามันคือการหลอกหลวง แล้วคนโกงจะได้อะไร [](https://stock.adobe.com/stock-photo/id/1010196295) อันดับแรกไปพิจารณาดู opensea ครับ เป็นเวบ NFTmarketplace ที่ volume การซื้อขายสูงที่สุด เขาไม่เก็บเงินของคนจะซื้อจะขายกันไว้กับตัวเอง เงินวิ่งเข้าวิ่งออก wallet ผู้ซื้อผู้ขายเลย ส่วนทางเวบเก็บค่าธรรมเนียมเท่านั้น แถมค่าธรรมเนียมก็ถูกกว่าเมื่อปี 2020 เยอะ ดังนั้นการที่จะไปลงขายงานบนเวบ NFT อื่นที่ค่า fee สูงกว่ากันเป็นร้อยเท่า ... จะทำไปทำไม ผมเชื่อว่า scammer โกงเงินเจ้าของผลงานโดยการเล่นกับความโลภและความอ่อนประสบการณ์ของเจ้าของผลงานครับ เมื่อไหร่ก็ตามที่เจ้าของผลงานโอน ETH เข้าไปใน wallet เวบนั้นเมื่อไหร่ หรือเมื่อไหร่ก็ตามที่จ่ายค่า fee ในการ mint งาน เงินเหล่านั้นสิ่งเข้ากระเป๋า scammer ทันที แล้วก็จะมีการเล่นตุกติกต่อแน่นอนครับ เช่นถอนไม่ได้ หรือซื้อไม่ได้ ต้องโอนเงินมาเพิ่มเพื่อปลดล็อค smart contract อะไรก็ว่าไป แล้วคนนิสัยไม่ดีพวกเนี้ย ก็จะเล่นกับความโลภของคน เอาราคาเสนอซื้อที่สูงโคตรๆมาล่อ ... อันนี้ไม่ว่ากัน เพราะบนโลก NFT รูปภาพบางรูปที่ไม่ได้มีความเป็นศิลปะอะไรเลย มันดันขายกันได้ 100 - 150 ETH ศิลปินที่พยายามสร้างตัวก็อาจจะมองว่า ผลงานเรามีคนรับซื้อ 2 - 4 ETH ต่องานมันก็มากพอแล้ว (จริงๆมากเกินจนน่าตกใจด้วยซ้ำครับ) บนโลกของ BTC ไม่ต้องเชื่อใจกัน โอนเงินไปหากันได้ ปิดสมุดบัญชีได้โดยไม่ต้องเชื่อใจกัน บบโลกของ ETH **"code is law"** smart contract มีเขียนอยู่แล้ว ไปอ่าน มันไม่ได้ยากมากในการทำความเข้าใจ ดังนั้น การจะมาเชื่อคำสัญญาจากคนด้วยกัน เป็นอะไรที่ไม่มีเหตุผล ผมไปเล่าเรื่องเหล่านี้ให้กับ community งานศิลปะ ก็มีทั้งเสียงตอบรับที่ดี และไม่ดีปนกันไป มีบางคนยืนยันเสียงแข็งไปในทำนองว่า ไอ้เรื่องแบบเนี้ยไม่ได้กินเขาหรอก เพราะเขาตั้งใจแน่วแน่ว่างานศิลป์ของเขา เขาไม่เอาเข้ามายุ่งในโลก digital currency เด็ดขาด ซึ่งผมก็เคารพมุมมองเขาครับ แต่มันจะดีกว่ามั้ย ถ้าเราเปิดหูเปิดตาให้ทันเทคโนโลยี โดยเฉพาะเรื่อง digital currency , blockchain โดนโกงทีนึงนี่คือหมดตัวกันง่ายกว่าเงิน fiat อีก อยากจะมาเล่าให้ฟังครับ และอยากให้ช่วยแชร์ไปให้คนรู้จักด้วย จะได้ระวังตัวกัน ## Note - ภาพประกอบ cyber security ทั้งสองนี่ของผมเองครับ ทำเอง วางขายบน AdobeStock - อีกบัญชีนึงของผม "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw กำลังค่อยๆเอาผลงานจากโลกข้างนอกเข้ามา nostr ครับ ตั้งใจจะมาสร้างงานศิลปะในนี้ เพื่อนๆที่ชอบงาน จะได้ไม่ต้องออกไปหาที่ไหน ผลงานของผมครับ - Anime girl fanarts : [HikariHarmony](https://linktr.ee/hikariharmonypatreon) - [HikariHarmony on Nostr](https://shorturl.at/I8Nu4) - General art : [KeshikiRakuen](https://linktr.ee/keshikirakuen) - KeshikiRakuen อาจจะเป็นบัญชี nostr ที่สามของผม ถ้าไหวครับ @ 8947a945:9bfcf626
2024-10-17 07:33:00[](https://stock.adobe.com/stock-photo/id/1010191703) **Hello everyone on Nostr** and all my **watchers**and **followers**from DeviantArt, as well as those from other art platforms I have been creating and sharing AI-generated anime girl fanart since the beginning of 2024 and have been running member-exclusive content on Patreon. I also publish showcases of my artworks to Deviantart. I organically build up my audience from time to time. I consider it as one of my online businesses of art. Everything is slowly growing **On September 16**, I received a DM from someone expressing interest in purchasing my art in NFT format and offering a very high price for each piece. We later continued the conversation via email.  ### Here’s a brief overview of what happened  - The first scammer selected the art they wanted to buy and offered a high price for each piece. They provided a URL to an NFT marketplace site running on the Ethereum (ETH) mainnet or ERC20. The site appeared suspicious, requiring email sign-up and linking a MetaMask wallet. However, I couldn't change the wallet address later. The minting gas fees were quite expensive, ranging from **0.15 to 0.2 ETH**  - The scammers tried to convince me that the high profits would easily cover the minting gas fees, so I had nothing to lose. Luckily, I didn’t have spare funds to purchase ETH for the gas fees at the time, so I tried negotiating with them as follows: 1. I offered to send them a lower-quality version of my art via email in exchange for the minting gas fees, but they refused. 2. I offered them the option to pay in USD through Buy Me a Coffee shop here, but they refused. 3. I offered them the option to pay via Bitcoin using the Lightning Network invoice , but they refused. 4. I asked them to wait until I could secure the funds, and they agreed to wait. The following week, a second scammer approached me with a similar offer, this time at an even higher price and through a different NFT marketplace website. This second site also required email registration, and after navigating to the dashboard, it asked for a minting fee of **0.2 ETH**. However, the site provided a wallet address for me instead of connecting a MetaMask wallet. I told the second scammer that I was waiting to make a profit from the first sale, and they asked me to show them the first marketplace. They then warned me that the first site was a scam and even sent screenshots of victims, including one from OpenSea saying that Opensea is not paying. **This raised a red flag**, and I began suspecting I might be getting scammed. On OpenSea, funds go directly to users' wallets after transactions, and OpenSea charges a much lower platform fee compared to the previous crypto bull run in 2020. Minting fees on OpenSea are also significantly cheaper, around 0.0001 ETH per transaction. I also consulted with Thai NFT artist communities and the ex-chairman of the Thai Digital Asset Association. According to them, no one had reported similar issues, but they agreed it seemed like a scam. After confirming my suspicions with my own research and consulting with the Thai crypto community, I decided to test the scammers’ intentions by doing the following I minted the artwork they were interested in, set the price they offered, and listed it for sale on OpenSea. I then messaged them, letting them know the art was available and ready to purchase, with no royalty fees if they wanted to resell it. They became upset and angry, insisting I mint the art on their chosen platform, claiming they had already funded their wallet to support me. When I asked for proof of their wallet address and transactions, they couldn't provide any evidence that they had enough funds. Here’s what I want to warn all artists in the DeviantArt community or other platforms If you find yourself in a similar situation, be aware that scammers may be targeting you. ----------- ### My Perspective why I Believe This is a Scam and What the Scammers Gain [](https://stock.adobe.com/stock-photo/id/1010196295) From my experience with BTC and crypto since 2017, here's why I believe this situation is a scam, and what the scammers aim to achieve First, looking at OpenSea, the largest NFT marketplace on the ERC20 network, they do not hold users' funds. Instead, funds from transactions go directly to users’ wallets. OpenSea’s platform fees are also much lower now compared to the crypto bull run in 2020. This alone raises suspicion about the legitimacy of other marketplaces requiring significantly higher fees. I believe the scammers' tactic is to lure artists into paying these exorbitant minting fees, which go directly into the scammers' wallets. They convince the artists by promising to purchase the art at a higher price, making it seem like there's no risk involved. In reality, the artist has already lost by paying the minting fee, and no purchase is ever made. In the world of Bitcoin (BTC), the principle is "Trust no one" and “Trustless finality of transactions” In other words, transactions are secure and final without needing trust in a third party. In the world of Ethereum (ETH), the philosophy is "Code is law" where everything is governed by smart contracts deployed on the blockchain. These contracts are transparent, and even basic code can be read and understood. Promises made by people don’t override what the code says. I also discuss this issue with art communities. Some people have strongly expressed to me that they want nothing to do with crypto as part of their art process. I completely respect that stance. However, I believe it's wise to keep your eyes open, have some skin in the game, and not fall into scammers’ traps. Understanding the basics of crypto and NFTs can help protect you from these kinds of schemes. If you found this article helpful, please share it with your fellow artists. Until next time Take care ## Note - Both cyber security images are mine , I created and approved by AdobeStock to put on sale - I'm working very hard to bring all my digital arts into Nostr to build my Sats business here to my another npub "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw Link to my full gallery - Anime girl fanarts : [HikariHarmony](https://linktr.ee/hikariharmonypatreon) - [HikariHarmony on Nostr](https://shorturl.at/I8Nu4) - General art : [KeshikiRakuen](https://linktr.ee/keshikirakuen)
@ 8947a945:9bfcf626
2024-10-17 07:33:00[](https://stock.adobe.com/stock-photo/id/1010191703) **Hello everyone on Nostr** and all my **watchers**and **followers**from DeviantArt, as well as those from other art platforms I have been creating and sharing AI-generated anime girl fanart since the beginning of 2024 and have been running member-exclusive content on Patreon. I also publish showcases of my artworks to Deviantart. I organically build up my audience from time to time. I consider it as one of my online businesses of art. Everything is slowly growing **On September 16**, I received a DM from someone expressing interest in purchasing my art in NFT format and offering a very high price for each piece. We later continued the conversation via email.  ### Here’s a brief overview of what happened  - The first scammer selected the art they wanted to buy and offered a high price for each piece. They provided a URL to an NFT marketplace site running on the Ethereum (ETH) mainnet or ERC20. The site appeared suspicious, requiring email sign-up and linking a MetaMask wallet. However, I couldn't change the wallet address later. The minting gas fees were quite expensive, ranging from **0.15 to 0.2 ETH**  - The scammers tried to convince me that the high profits would easily cover the minting gas fees, so I had nothing to lose. Luckily, I didn’t have spare funds to purchase ETH for the gas fees at the time, so I tried negotiating with them as follows: 1. I offered to send them a lower-quality version of my art via email in exchange for the minting gas fees, but they refused. 2. I offered them the option to pay in USD through Buy Me a Coffee shop here, but they refused. 3. I offered them the option to pay via Bitcoin using the Lightning Network invoice , but they refused. 4. I asked them to wait until I could secure the funds, and they agreed to wait. The following week, a second scammer approached me with a similar offer, this time at an even higher price and through a different NFT marketplace website. This second site also required email registration, and after navigating to the dashboard, it asked for a minting fee of **0.2 ETH**. However, the site provided a wallet address for me instead of connecting a MetaMask wallet. I told the second scammer that I was waiting to make a profit from the first sale, and they asked me to show them the first marketplace. They then warned me that the first site was a scam and even sent screenshots of victims, including one from OpenSea saying that Opensea is not paying. **This raised a red flag**, and I began suspecting I might be getting scammed. On OpenSea, funds go directly to users' wallets after transactions, and OpenSea charges a much lower platform fee compared to the previous crypto bull run in 2020. Minting fees on OpenSea are also significantly cheaper, around 0.0001 ETH per transaction. I also consulted with Thai NFT artist communities and the ex-chairman of the Thai Digital Asset Association. According to them, no one had reported similar issues, but they agreed it seemed like a scam. After confirming my suspicions with my own research and consulting with the Thai crypto community, I decided to test the scammers’ intentions by doing the following I minted the artwork they were interested in, set the price they offered, and listed it for sale on OpenSea. I then messaged them, letting them know the art was available and ready to purchase, with no royalty fees if they wanted to resell it. They became upset and angry, insisting I mint the art on their chosen platform, claiming they had already funded their wallet to support me. When I asked for proof of their wallet address and transactions, they couldn't provide any evidence that they had enough funds. Here’s what I want to warn all artists in the DeviantArt community or other platforms If you find yourself in a similar situation, be aware that scammers may be targeting you. ----------- ### My Perspective why I Believe This is a Scam and What the Scammers Gain [](https://stock.adobe.com/stock-photo/id/1010196295) From my experience with BTC and crypto since 2017, here's why I believe this situation is a scam, and what the scammers aim to achieve First, looking at OpenSea, the largest NFT marketplace on the ERC20 network, they do not hold users' funds. Instead, funds from transactions go directly to users’ wallets. OpenSea’s platform fees are also much lower now compared to the crypto bull run in 2020. This alone raises suspicion about the legitimacy of other marketplaces requiring significantly higher fees. I believe the scammers' tactic is to lure artists into paying these exorbitant minting fees, which go directly into the scammers' wallets. They convince the artists by promising to purchase the art at a higher price, making it seem like there's no risk involved. In reality, the artist has already lost by paying the minting fee, and no purchase is ever made. In the world of Bitcoin (BTC), the principle is "Trust no one" and “Trustless finality of transactions” In other words, transactions are secure and final without needing trust in a third party. In the world of Ethereum (ETH), the philosophy is "Code is law" where everything is governed by smart contracts deployed on the blockchain. These contracts are transparent, and even basic code can be read and understood. Promises made by people don’t override what the code says. I also discuss this issue with art communities. Some people have strongly expressed to me that they want nothing to do with crypto as part of their art process. I completely respect that stance. However, I believe it's wise to keep your eyes open, have some skin in the game, and not fall into scammers’ traps. Understanding the basics of crypto and NFTs can help protect you from these kinds of schemes. If you found this article helpful, please share it with your fellow artists. Until next time Take care ## Note - Both cyber security images are mine , I created and approved by AdobeStock to put on sale - I'm working very hard to bring all my digital arts into Nostr to build my Sats business here to my another npub "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw Link to my full gallery - Anime girl fanarts : [HikariHarmony](https://linktr.ee/hikariharmonypatreon) - [HikariHarmony on Nostr](https://shorturl.at/I8Nu4) - General art : [KeshikiRakuen](https://linktr.ee/keshikirakuen) @ 472f440f:5669301e
2024-10-16 01:57:41Over the last four years bitcoin has, among other things, established itself as an incredible corporate treasury asset that benefits those who adopt it as such. Microstrategy is the shining example of this theme going from a company that was hovering barely above a ~$1B market cap in mid-2020 to a ~$40B market cap company holding more than 1% of the 21,000,000 bitcoin that will ever exist. Microstrategy's success has emboldened a number of other publicly trader companies to follow suit. Bitcoin as a corporate treasury asset is well on its way to becoming a standard. If you run a business that doesn't hold bitcoin on its balance sheet you are doing yourself, your customers and your shareholders a disservice. This is a trend that has its legs under it and will accelerate moving forward. A trend that I believe will emerge this cycle is incorporating bitcoin into real estate markets. Leon Wankum has been beating the drum about this for the last few years and I had the pleasure of sitting down with him this morning to record an episode of TFTC that will be published tomorrow morning. Leon is a real estate developer in Germany and he has made it his mission to educate and warn others in real estate about the demonetization of real estate that is under way due to the fact that bitcoin exists and it provides a far superior alternative. These are pretty stark numbers. Nothing highlights the superior monetary properties of bitcoin better than looking at a chart of the average price of a home priced in USD v. bitcoin. Since 2016: +46% in USD -99% in BTC Since 2020: +34% in USD -70% in BTC The funny thing is that an overwhelming majority of the individuals who make their living in real estate markets do not understand that this is happening to them. Many think they are doing exceptionally well all things considered. Sure, there may be a bit of a slow down and price retraction due to a couple of years of relatively elevated interest rates, but don't worry! The Fed is lowering rates again and the good times are about to start back up. Nothing could be further from the truth. This trend is going to continue unabated until bitcoin is fully monetized and those is the real estate industry, particularly real estate developers and those who lend capital to developers, should seriously take the time to understand what is happening to them. Real estate is the largest store of value asset in the world at the moment. The most common number that is thrown around for the total size of the market is $300 TRILLION. $300 TRILLION of wealth being stored in an asset that is illiquid, comes with maintenance costs, taxes, insurance premiums, and susceptible to extreme weather event, among other things. Compared to bitcoin - which is extremely liquid, saleable, divisible and hard to confiscate, real estate is a far superior asset to store your wealth in. This is something that I'm sure is well understood by many of you reading this letter. What's less understood is the dynamics of the real estate development market over the last few years, which have been severely hindered by elevated interest rates. The higher interest rate environment coupled with the inflationary pressures that forced rates higher in the first place have put developers in a predicament; they have a higher cost of capital to start new projects with raw material prices that are still much higher than they were before the economic lock downs of 2020-2022. This has led to a scenario where it isn't advantageous to start new projects and the projects that broke ground in 2021-2023 are finding that they need to incur more debt to get their developments across the finish line. Despite the fact that interest rates are on their way back down, it doesn't seem like the economics of these projects are going to materially improve in the short to medium-term as headline inflation begins to creep back up. Couple this with the fact that the jobs market is cratering while real wages struggle to keep up with inflation and many builders are going to find themselves in a situation where they do actually complete a development problem but their cash flow suffers because their customers can't afford the inflated rents that builders will have to charge to get a return on their outlaid capital. Many will be put in a situation where they are forced to be happy with lower rents (cash flow) or sit on the sidelines making no cash flow. The post-1971 era that brought with it a booming real estate industry is suffering the same fate as the bond market; the generation bull market is over. Real estate prices may go up, but that will be nothing more than a mirage of wealth creation. The unit of account those prices are built on is in dollars, which are being debased at an accelerating rate. Developers, banks and borrowers need to de-risk their real estate exposure and, as Leon points out, bitcoin is the only way to do this in an effective way. Moving forward developers will have to finance by dual collateralizing their debt with the real estate and bitcoin. In the graphic below Leon illustrates what this type of financing structure will look like. Instead of taking $10m of debt to finance a project and putting it all into materials, construction and marketing, a developer will take out a $10m loan, put $1m in bitcoin and the rest toward the development project. Over the course of the construction of the real estate project, bitcoin will sit in the credit structure and, if held for 4+ years, should increase significantly in value. Saving the builder from risk of default and providing him some optionality in terms of what he can do with the project once it's finished. In this scenario downside risk is contained - a developer isn't pouring all of the cash into bitcoin at the beginning so the worst case scenario is that bitcoin goes to zero (highly unlikely) and they can eat the small loss and hope to make up with it via cash flows once a project is finished, while upside potential is enormous. Bitcoin is still monetizing and having exposure to the hardest monetary asset the world has ever while it's monetizing has proven to be massively beneficial. We are still in the early days of bitcoin and this idea will likely seem absolutely insane to most Tradfi investors, but I strongly believe that developers, banks and end consumers who don't leverage this type of bitcoin structured credit will be cooked in the long-run. And those that take advantage of this type of structure first will be considered geniuses in 20 years. There are many more nuanced benefits to this strategy; holding bitcoin allows landlords and management companies to weather ongoing maintenance costs throughout the years, those who take out mortgages dual collateralized with a house and bitcoin not only protect the equity value of their property but could see their equity values increase significantly more than others using vanilla mortgages, and builders who accumulate bitcoin in their treasuries will be able to use better raw materials when building, which leads to more valuable properties that cash flow for longer. Again, it's going to take time for these types of structures to become commonplace in the market, but I firmly believe this cycle will be the cycle that these strategies get off the ground. In four to five years they will have a track record and after that it will be considered irresponsible not to finance real estate in this way. The banks will begin to demand it. --- Final thought... Sinus congestion sucks.
@ 472f440f:5669301e
2024-10-16 01:57:41Over the last four years bitcoin has, among other things, established itself as an incredible corporate treasury asset that benefits those who adopt it as such. Microstrategy is the shining example of this theme going from a company that was hovering barely above a ~$1B market cap in mid-2020 to a ~$40B market cap company holding more than 1% of the 21,000,000 bitcoin that will ever exist. Microstrategy's success has emboldened a number of other publicly trader companies to follow suit. Bitcoin as a corporate treasury asset is well on its way to becoming a standard. If you run a business that doesn't hold bitcoin on its balance sheet you are doing yourself, your customers and your shareholders a disservice. This is a trend that has its legs under it and will accelerate moving forward. A trend that I believe will emerge this cycle is incorporating bitcoin into real estate markets. Leon Wankum has been beating the drum about this for the last few years and I had the pleasure of sitting down with him this morning to record an episode of TFTC that will be published tomorrow morning. Leon is a real estate developer in Germany and he has made it his mission to educate and warn others in real estate about the demonetization of real estate that is under way due to the fact that bitcoin exists and it provides a far superior alternative. These are pretty stark numbers. Nothing highlights the superior monetary properties of bitcoin better than looking at a chart of the average price of a home priced in USD v. bitcoin. Since 2016: +46% in USD -99% in BTC Since 2020: +34% in USD -70% in BTC The funny thing is that an overwhelming majority of the individuals who make their living in real estate markets do not understand that this is happening to them. Many think they are doing exceptionally well all things considered. Sure, there may be a bit of a slow down and price retraction due to a couple of years of relatively elevated interest rates, but don't worry! The Fed is lowering rates again and the good times are about to start back up. Nothing could be further from the truth. This trend is going to continue unabated until bitcoin is fully monetized and those is the real estate industry, particularly real estate developers and those who lend capital to developers, should seriously take the time to understand what is happening to them. Real estate is the largest store of value asset in the world at the moment. The most common number that is thrown around for the total size of the market is $300 TRILLION. $300 TRILLION of wealth being stored in an asset that is illiquid, comes with maintenance costs, taxes, insurance premiums, and susceptible to extreme weather event, among other things. Compared to bitcoin - which is extremely liquid, saleable, divisible and hard to confiscate, real estate is a far superior asset to store your wealth in. This is something that I'm sure is well understood by many of you reading this letter. What's less understood is the dynamics of the real estate development market over the last few years, which have been severely hindered by elevated interest rates. The higher interest rate environment coupled with the inflationary pressures that forced rates higher in the first place have put developers in a predicament; they have a higher cost of capital to start new projects with raw material prices that are still much higher than they were before the economic lock downs of 2020-2022. This has led to a scenario where it isn't advantageous to start new projects and the projects that broke ground in 2021-2023 are finding that they need to incur more debt to get their developments across the finish line. Despite the fact that interest rates are on their way back down, it doesn't seem like the economics of these projects are going to materially improve in the short to medium-term as headline inflation begins to creep back up. Couple this with the fact that the jobs market is cratering while real wages struggle to keep up with inflation and many builders are going to find themselves in a situation where they do actually complete a development problem but their cash flow suffers because their customers can't afford the inflated rents that builders will have to charge to get a return on their outlaid capital. Many will be put in a situation where they are forced to be happy with lower rents (cash flow) or sit on the sidelines making no cash flow. The post-1971 era that brought with it a booming real estate industry is suffering the same fate as the bond market; the generation bull market is over. Real estate prices may go up, but that will be nothing more than a mirage of wealth creation. The unit of account those prices are built on is in dollars, which are being debased at an accelerating rate. Developers, banks and borrowers need to de-risk their real estate exposure and, as Leon points out, bitcoin is the only way to do this in an effective way. Moving forward developers will have to finance by dual collateralizing their debt with the real estate and bitcoin. In the graphic below Leon illustrates what this type of financing structure will look like. Instead of taking $10m of debt to finance a project and putting it all into materials, construction and marketing, a developer will take out a $10m loan, put $1m in bitcoin and the rest toward the development project. Over the course of the construction of the real estate project, bitcoin will sit in the credit structure and, if held for 4+ years, should increase significantly in value. Saving the builder from risk of default and providing him some optionality in terms of what he can do with the project once it's finished. In this scenario downside risk is contained - a developer isn't pouring all of the cash into bitcoin at the beginning so the worst case scenario is that bitcoin goes to zero (highly unlikely) and they can eat the small loss and hope to make up with it via cash flows once a project is finished, while upside potential is enormous. Bitcoin is still monetizing and having exposure to the hardest monetary asset the world has ever while it's monetizing has proven to be massively beneficial. We are still in the early days of bitcoin and this idea will likely seem absolutely insane to most Tradfi investors, but I strongly believe that developers, banks and end consumers who don't leverage this type of bitcoin structured credit will be cooked in the long-run. And those that take advantage of this type of structure first will be considered geniuses in 20 years. There are many more nuanced benefits to this strategy; holding bitcoin allows landlords and management companies to weather ongoing maintenance costs throughout the years, those who take out mortgages dual collateralized with a house and bitcoin not only protect the equity value of their property but could see their equity values increase significantly more than others using vanilla mortgages, and builders who accumulate bitcoin in their treasuries will be able to use better raw materials when building, which leads to more valuable properties that cash flow for longer. Again, it's going to take time for these types of structures to become commonplace in the market, but I firmly believe this cycle will be the cycle that these strategies get off the ground. In four to five years they will have a track record and after that it will be considered irresponsible not to finance real estate in this way. The banks will begin to demand it. --- Final thought... Sinus congestion sucks. @ eac63075:b4988b48
2024-10-15 20:18:52Bitcoin emerged as a promise of financial freedom, challenging the traditional and centralized structures of governments and financial institutions. Since its inception, many enthusiasts have believed in the revolutionary potential of this cryptocurrency. However, over the years, challenges have arisen that have tested this promise, especially concerning centralization, the implementation of secondary layers like the Lightning Network, and issues of governance and privacy. https://www.fountain.fm/episode/SDZYaFMyLEO1krL6x8RD ## **Centralization and the Exclusivity of Nostr** Nostr, a decentralized network aiming to be censorship resistant, emerged as an attempt to solve some inherent problems of centralization. However, it faces significant challenges. Many users point out that, despite its promise, Nostr is still not attractive to the general public, being exclusive to a specific niche. Additionally, issues of centralization still permeate the network. Discussions on GitHub revealed that developers chose not to implement an absolute level of privacy, a decision many considered inadequate. Even with protocols developed to ensure total privacy—such as the non-identification of IPs and communicating parties—the network still lacks this robust implementation. ## **Individual Freedom and Data Protection** A recurring issue is the importance of demonstrating that real options exist for citizens to protect and preserve their freedom. In a world where most discussions about Bitcoin revolve around its use as an investment asset, there is an urgent need to emphasize its potential as a tool for financial freedom. The Bitcoin community should focus on development and education, showing that the conscious use of cryptography and decentralized transactions can protect individuals against excessive government surveillance and control. Secure and private communication is fundamental, and Bitcoin, along with privacy technologies, can provide this. ## **Hyperbitcoinization and the Illusion of Store of Value** Hyperbitcoinization is a concept that refers to the moment when Bitcoin will replace fiat currencies worldwide. However, achieving this state is not simple, especially when Bitcoin is seen primarily as a store of value. Since 2017, this narrative has gained strength, promoting the idea that accumulating Bitcoin will lead to automatic wealth. However, this perspective is limited. The true value of Bitcoin lies in its use as a transactional currency, not just in its scarcity. The community must work to ensure that Bitcoin is utilized in everyday transactions, strengthening its network and demonstrating its real value. ## **The Role of the Community in Bitcoin's Development** Bitcoin's strength comes from its community. Developers, users, and enthusiasts, through their actions and support, make Bitcoin a powerful tool. This community is responsible for ensuring that Bitcoin maintains its essence and that its functionalities are accessible to all. It is crucial that this support network continues promoting the decentralized use of Bitcoin, without intermediaries that can censor or control transactions. Adopting Bitcoin in a centralized manner, through banks or other institutions, contradicts its original proposal and strengthens those who have historically opposed its existence. ## **Sidechains, Second Layers, and the Lightning Network** Sidechains and second layers, like the Lightning Network, are essential components for Bitcoin's scalability. However, they bring challenges, especially regarding the need to trust intermediaries. For these solutions to be effective, it is fundamental that they allow the unilateral withdrawal of funds, ensuring that users maintain full control over their assets. The Lightning Network, for example, is a second layer that allows fast and cheap transactions. However, many users face difficulties when dealing with channels that do not close correctly, resulting in locked funds. These problems must be solved for the network to be truly decentralized and functional. ## **The Fight Against Centralization on the Internet** Centralization is not a problem exclusive to Bitcoin. The internet as a whole faces similar challenges, with data control concentrated in the hands of a few large technology companies. To ensure freedom of expression and online privacy, it is necessary to decentralize these data clusters. Projects that seek to decentralize the internet are vital for this mission. They not only complement Bitcoin in its quest for financial freedom but also ensure that digital communication and expression are protected against censorship and corporate control. ## **The Future of Bitcoin and the Need for Action** The future of Bitcoin depends on the community's action. We cannot expect Bitcoin to automatically become a global medium of exchange. A conscious effort is necessary to build an ecosystem where Bitcoin can flow freely, being used in everyday transactions and valued for its utility. Moreover, with the imminent arrival of central bank digital currencies (CBDCs), time is of the essence. CBDCs represent a significant challenge, as they can further restrict individuals' financial freedom. Therefore, accelerating Bitcoin adoption and ensuring it maintains its decentralized and uncensorable properties is a priority. ## **Conclusion** Bitcoin remains a powerful tool for financial freedom but faces significant challenges. Centralization, both in the context of secondary networks and the internet in general, poses a threat to its original proposal. However, with the joint action of the community and the continuous development of decentralized solutions, it is possible to maintain Bitcoin as a bastion of individual freedom. The true revolution of Bitcoin lies in its use as a medium of exchange, not just as a store of value. To achieve hyperbitcoinization, it is necessary to build a robust ecosystem where Bitcoin can circulate freely and be accessible to all. Only then can we fulfill Bitcoin's initial promise and ensure it continues to be a tool for freedom and financial autonomy.
@ eac63075:b4988b48
2024-10-15 20:18:52Bitcoin emerged as a promise of financial freedom, challenging the traditional and centralized structures of governments and financial institutions. Since its inception, many enthusiasts have believed in the revolutionary potential of this cryptocurrency. However, over the years, challenges have arisen that have tested this promise, especially concerning centralization, the implementation of secondary layers like the Lightning Network, and issues of governance and privacy. https://www.fountain.fm/episode/SDZYaFMyLEO1krL6x8RD ## **Centralization and the Exclusivity of Nostr** Nostr, a decentralized network aiming to be censorship resistant, emerged as an attempt to solve some inherent problems of centralization. However, it faces significant challenges. Many users point out that, despite its promise, Nostr is still not attractive to the general public, being exclusive to a specific niche. Additionally, issues of centralization still permeate the network. Discussions on GitHub revealed that developers chose not to implement an absolute level of privacy, a decision many considered inadequate. Even with protocols developed to ensure total privacy—such as the non-identification of IPs and communicating parties—the network still lacks this robust implementation. ## **Individual Freedom and Data Protection** A recurring issue is the importance of demonstrating that real options exist for citizens to protect and preserve their freedom. In a world where most discussions about Bitcoin revolve around its use as an investment asset, there is an urgent need to emphasize its potential as a tool for financial freedom. The Bitcoin community should focus on development and education, showing that the conscious use of cryptography and decentralized transactions can protect individuals against excessive government surveillance and control. Secure and private communication is fundamental, and Bitcoin, along with privacy technologies, can provide this. ## **Hyperbitcoinization and the Illusion of Store of Value** Hyperbitcoinization is a concept that refers to the moment when Bitcoin will replace fiat currencies worldwide. However, achieving this state is not simple, especially when Bitcoin is seen primarily as a store of value. Since 2017, this narrative has gained strength, promoting the idea that accumulating Bitcoin will lead to automatic wealth. However, this perspective is limited. The true value of Bitcoin lies in its use as a transactional currency, not just in its scarcity. The community must work to ensure that Bitcoin is utilized in everyday transactions, strengthening its network and demonstrating its real value. ## **The Role of the Community in Bitcoin's Development** Bitcoin's strength comes from its community. Developers, users, and enthusiasts, through their actions and support, make Bitcoin a powerful tool. This community is responsible for ensuring that Bitcoin maintains its essence and that its functionalities are accessible to all. It is crucial that this support network continues promoting the decentralized use of Bitcoin, without intermediaries that can censor or control transactions. Adopting Bitcoin in a centralized manner, through banks or other institutions, contradicts its original proposal and strengthens those who have historically opposed its existence. ## **Sidechains, Second Layers, and the Lightning Network** Sidechains and second layers, like the Lightning Network, are essential components for Bitcoin's scalability. However, they bring challenges, especially regarding the need to trust intermediaries. For these solutions to be effective, it is fundamental that they allow the unilateral withdrawal of funds, ensuring that users maintain full control over their assets. The Lightning Network, for example, is a second layer that allows fast and cheap transactions. However, many users face difficulties when dealing with channels that do not close correctly, resulting in locked funds. These problems must be solved for the network to be truly decentralized and functional. ## **The Fight Against Centralization on the Internet** Centralization is not a problem exclusive to Bitcoin. The internet as a whole faces similar challenges, with data control concentrated in the hands of a few large technology companies. To ensure freedom of expression and online privacy, it is necessary to decentralize these data clusters. Projects that seek to decentralize the internet are vital for this mission. They not only complement Bitcoin in its quest for financial freedom but also ensure that digital communication and expression are protected against censorship and corporate control. ## **The Future of Bitcoin and the Need for Action** The future of Bitcoin depends on the community's action. We cannot expect Bitcoin to automatically become a global medium of exchange. A conscious effort is necessary to build an ecosystem where Bitcoin can flow freely, being used in everyday transactions and valued for its utility. Moreover, with the imminent arrival of central bank digital currencies (CBDCs), time is of the essence. CBDCs represent a significant challenge, as they can further restrict individuals' financial freedom. Therefore, accelerating Bitcoin adoption and ensuring it maintains its decentralized and uncensorable properties is a priority. ## **Conclusion** Bitcoin remains a powerful tool for financial freedom but faces significant challenges. Centralization, both in the context of secondary networks and the internet in general, poses a threat to its original proposal. However, with the joint action of the community and the continuous development of decentralized solutions, it is possible to maintain Bitcoin as a bastion of individual freedom. The true revolution of Bitcoin lies in its use as a medium of exchange, not just as a store of value. To achieve hyperbitcoinization, it is necessary to build a robust ecosystem where Bitcoin can circulate freely and be accessible to all. Only then can we fulfill Bitcoin's initial promise and ensure it continues to be a tool for freedom and financial autonomy. @ 599f67f7:21fb3ea9
2024-10-14 19:36:50Inoiz pentsatu al duzu norbaiti satoshiak modu originalean oparitzea, Bitcoin mundura hurbiltzeko? LNbits zorro batekin NFC opari txartel bat erraz sor dezakezu. Honek LNURLw esteka bat NFC txartelean idatziz funtzionatzen du, eta jasotzaileak bere satoshiak erabili ditzake LNURL gaitutako zorro batekin. ### Zer behar dut? - LNbits zorroa - Android telefono bat - NTAG2* gaitasunak dituen NFC txartela, adibidez NTAG216. 💡 NTAG2* txartelek esteka **bat** idazteko aukera ematen dute. Adibidez, enpresaren webgunerako URLa duen bisita-txartel gisa joka dezakete. NTAG424 txartelek ez dute memoria handiagoa bakarrik, baizik eta SUN parametro deitzen den zerbait ere badute, zerbitzariaren autentifikazioa ahalbidetzen duena, eta horrek segurtasun gehiago ematen die zure ordainketei. Azkenean txartel mota hau [BoltCard](https://boltcard.org/) bat bihur daiteke. ### 1. Hedapena aktibatu Ireki zure LNbits zorroa. Tresna-barran, aktibatu `Withdraw Links` hedapena eta ondoren joan hedapenera. ### 2. Erretiratzeko esteka sortu `Withdraw Links` hedapen orrian, aukeratu `Advanced Withdraw Link(s)` aukera. Ondoren, aukeratu satoshiak ateratzeko erabiliko duzun zorroa. Ziurrenik, hori zure LNbits zorro nagusitik bereizi nahi izango duzu. Horretarako, LNbits zorro berri bat sor dezakezu tresna-barratik, `+ Add a new wallet` aukera hautatuz. Behin zorro berria sortuta, sartu satoshi batzuk bertan.  Eman izenburu bat erretiratzeko estekari. Ezarri erreskatatu daitezkeen gutxieneko eta gehienezko zenbatekoak. Ezarri esteka zenbat aldiz erabil daitekeen eta erretiratze saiakeren arteko denbora. Aukeran, argazki pertsonalizatu bat gehi dezakezu `Use a custom voucher design` laukitxoa markatuz, eta .png irudi baten URL-a sartuz. Gogoan izan “assmilking” laukitxoa ez markatzea. Konfigurazioa amaitu ondoren, jarraitu erretiratzeko esteka sortzera. ### 3. Idatzi esteka NFC txartelean Zure erretiratzeko esteka berrian, klikatu `View LNURL` estekan. Ondoren, sakatu `Write to NFC` botoia eta eutsi NFC txartela telefonoaren aurrean idazketa-prozesua burutzeko.  ✔️ **EGINDA** 💡 Esan txartelaren jasotzaileari satoshi saldoari buruz, denbora ez dezan galdu azkeneko satoshia lortzen saiatzeko. 💡 Jasotzaileak txartelaren satoshiak atera ondoren, bere zorroan berridatzi dezake eta berrerabili. Gainera, eman diozun txartela NTAG424 bada, aurreko gidako (nostr:naddr1qqxnzd3e8qcr2wfn8qcrgwf4qyg8wumn8ghj7mn0wd68ytnhd9hx2q3qtx0k0a7lw62vvqax6p3ku90tccgdka7ul4radews2wrdsg0m865sxpqqqp65whwqrr5) bezala Lightning "zor txartela" bihur dezake. Baina txartela NTAG2* bakarrik bada, beste opari txartel bat bihur dezake soilik.
@ 599f67f7:21fb3ea9
2024-10-14 19:36:50Inoiz pentsatu al duzu norbaiti satoshiak modu originalean oparitzea, Bitcoin mundura hurbiltzeko? LNbits zorro batekin NFC opari txartel bat erraz sor dezakezu. Honek LNURLw esteka bat NFC txartelean idatziz funtzionatzen du, eta jasotzaileak bere satoshiak erabili ditzake LNURL gaitutako zorro batekin. ### Zer behar dut? - LNbits zorroa - Android telefono bat - NTAG2* gaitasunak dituen NFC txartela, adibidez NTAG216. 💡 NTAG2* txartelek esteka **bat** idazteko aukera ematen dute. Adibidez, enpresaren webgunerako URLa duen bisita-txartel gisa joka dezakete. NTAG424 txartelek ez dute memoria handiagoa bakarrik, baizik eta SUN parametro deitzen den zerbait ere badute, zerbitzariaren autentifikazioa ahalbidetzen duena, eta horrek segurtasun gehiago ematen die zure ordainketei. Azkenean txartel mota hau [BoltCard](https://boltcard.org/) bat bihur daiteke. ### 1. Hedapena aktibatu Ireki zure LNbits zorroa. Tresna-barran, aktibatu `Withdraw Links` hedapena eta ondoren joan hedapenera. ### 2. Erretiratzeko esteka sortu `Withdraw Links` hedapen orrian, aukeratu `Advanced Withdraw Link(s)` aukera. Ondoren, aukeratu satoshiak ateratzeko erabiliko duzun zorroa. Ziurrenik, hori zure LNbits zorro nagusitik bereizi nahi izango duzu. Horretarako, LNbits zorro berri bat sor dezakezu tresna-barratik, `+ Add a new wallet` aukera hautatuz. Behin zorro berria sortuta, sartu satoshi batzuk bertan.  Eman izenburu bat erretiratzeko estekari. Ezarri erreskatatu daitezkeen gutxieneko eta gehienezko zenbatekoak. Ezarri esteka zenbat aldiz erabil daitekeen eta erretiratze saiakeren arteko denbora. Aukeran, argazki pertsonalizatu bat gehi dezakezu `Use a custom voucher design` laukitxoa markatuz, eta .png irudi baten URL-a sartuz. Gogoan izan “assmilking” laukitxoa ez markatzea. Konfigurazioa amaitu ondoren, jarraitu erretiratzeko esteka sortzera. ### 3. Idatzi esteka NFC txartelean Zure erretiratzeko esteka berrian, klikatu `View LNURL` estekan. Ondoren, sakatu `Write to NFC` botoia eta eutsi NFC txartela telefonoaren aurrean idazketa-prozesua burutzeko.  ✔️ **EGINDA** 💡 Esan txartelaren jasotzaileari satoshi saldoari buruz, denbora ez dezan galdu azkeneko satoshia lortzen saiatzeko. 💡 Jasotzaileak txartelaren satoshiak atera ondoren, bere zorroan berridatzi dezake eta berrerabili. Gainera, eman diozun txartela NTAG424 bada, aurreko gidako (nostr:naddr1qqxnzd3e8qcr2wfn8qcrgwf4qyg8wumn8ghj7mn0wd68ytnhd9hx2q3qtx0k0a7lw62vvqax6p3ku90tccgdka7ul4radews2wrdsg0m865sxpqqqp65whwqrr5) bezala Lightning "zor txartela" bihur dezake. Baina txartela NTAG2* bakarrik bada, beste opari txartel bat bihur dezake soilik. @ 5e5fc143:393d5a2c
2024-10-11 22:15:54We are now given a choice of digital freedom #nostr . Creativity for every nostrich is now unleashed from the cage of bigtech censorship , rules and algo. But freedom comes with responsibility so pick right one(s). I will try share here some learning experience both technical and also from fundamental point of view. Just wanted kick start this article n fill as we go like living reference document. Nostr itself is an application layer protocol that can used beyond just social media mirco or long blogging. Each nostr client heavily dependent on back-end servers call nostr "Relay servers" or in short "rs" or "relays" Relays can hosted anywhere in clearnet internet, onion net , vpn , i2p , nym Relays are controlled by their respective admins based NIP specs that they select to implement according to own decisions. Relays can have certain ToS (Terms of Service) Rules to adhered too. New users can choose and pick client or app (ios / android/ windows) with preset of relays in the simplest form , but other advanced users need to do a regular manual relay management. Relay management is an active regular task based on where when n how you are using. Relay list are saved within you npub profile backup file which can edited and broadcast anytime. Relay management is an active regular task based on where when and how you are using. Relay list always need to be updated time to time as and when needed. 2 Users MUST a common RELAY between them even if one only need to follow another. Occasionally you may notice certain npub accounts you are following already but cannot see frequent notes publish by them – one of cause maybe you not sharing a common relay Most nostr client applications has SETTINGS where user choose add/remove relays Also user choose which function to enable - READ or WRITE Relay list for your account is always saved within you npub profile backup file which can edited and broadcast anytime. Hence any app or browser when u login with you npub the same relay list will be enforced. There could valid reasons why u need have list for if you trying to save bandwidth and traveling. Functions in app.getcurrent.io and primal.net app for mobile apple or android are ideal for user traveling abroad and wanted to save bandwidth since relay management is done the providers in backend and saves hassle for basic usage. Remember if someone is selecting relay on your behalf then you may not be necessarily able to pull and get some specific and special content that you may need. Such providers like coracle and nostrid also give option to override the default relays they selected. Relay types: They can be categorized by various features or policy or technologies. FREE PUBLIC Relays vs PAID PUBLIC Relays PAID relays provide unrestricted access / write / filtering options than FREE relays but both are public clearnet relays. Just subscribing to PAID relays will not solve all problems unless you choose the relays properly and enable settings correctly. Private Replay or Tor Relays – normally not easily visible until unless someone tell you. You can also host own private relay not opened to internet of archive and back of your own notes. The technical landscape in nostr can be fast changing as more NIPs get proposed or updated. Relays admin can choose implement certain NIPs or not based on policy or technical limitations. Example NIP33 defines “long notes” aka blogs as you now reading this in habla site which #1 UI and site for "Editable" long notes – some relays donot implement or allow this. NIP07 is used for client authentication like nos2x and is implemented by all relays in fact. Nostr is so fasting changing-hence many links many broken Pushing long note again. To be continued again ... reference pics will added later also Hope this help you understand "why when what" to tune and maintain active set of proper relays. Relay Proxy, Relay aggregator or Relay multiplexer – Paid, Public, Free, Private, Event, Relays That’s all for now n more later ... Thank you 🙏 ! ⚡️ https://getalby.com/p/captjack ⚡️ PV 💜 🤙 References: https://habla.news/relays https://relay.exchange/ https://relays.vercel.app/ https://nostr.info/relays/ https://nostrudel.ninja/#/relays Related Articles: https://thebitcoinmanual.com/articles/types-nostr-relays/ nostr:naddr1qqd5c6t8dp6xu6twvukkvctnwss92jfqvehhygzwdaehguszyrtp7w79k045gq80mtnpdxjuzl9t7vjxk52rv80f888y5xsd5mh55qcyqqq823cf39s98 https://habla.news/u/current@getcurrent.io/1694434022411
@ 5e5fc143:393d5a2c
2024-10-11 22:15:54We are now given a choice of digital freedom #nostr . Creativity for every nostrich is now unleashed from the cage of bigtech censorship , rules and algo. But freedom comes with responsibility so pick right one(s). I will try share here some learning experience both technical and also from fundamental point of view. Just wanted kick start this article n fill as we go like living reference document. Nostr itself is an application layer protocol that can used beyond just social media mirco or long blogging. Each nostr client heavily dependent on back-end servers call nostr "Relay servers" or in short "rs" or "relays" Relays can hosted anywhere in clearnet internet, onion net , vpn , i2p , nym Relays are controlled by their respective admins based NIP specs that they select to implement according to own decisions. Relays can have certain ToS (Terms of Service) Rules to adhered too. New users can choose and pick client or app (ios / android/ windows) with preset of relays in the simplest form , but other advanced users need to do a regular manual relay management. Relay management is an active regular task based on where when n how you are using. Relay list are saved within you npub profile backup file which can edited and broadcast anytime. Relay management is an active regular task based on where when and how you are using. Relay list always need to be updated time to time as and when needed. 2 Users MUST a common RELAY between them even if one only need to follow another. Occasionally you may notice certain npub accounts you are following already but cannot see frequent notes publish by them – one of cause maybe you not sharing a common relay Most nostr client applications has SETTINGS where user choose add/remove relays Also user choose which function to enable - READ or WRITE Relay list for your account is always saved within you npub profile backup file which can edited and broadcast anytime. Hence any app or browser when u login with you npub the same relay list will be enforced. There could valid reasons why u need have list for if you trying to save bandwidth and traveling. Functions in app.getcurrent.io and primal.net app for mobile apple or android are ideal for user traveling abroad and wanted to save bandwidth since relay management is done the providers in backend and saves hassle for basic usage. Remember if someone is selecting relay on your behalf then you may not be necessarily able to pull and get some specific and special content that you may need. Such providers like coracle and nostrid also give option to override the default relays they selected. Relay types: They can be categorized by various features or policy or technologies. FREE PUBLIC Relays vs PAID PUBLIC Relays PAID relays provide unrestricted access / write / filtering options than FREE relays but both are public clearnet relays. Just subscribing to PAID relays will not solve all problems unless you choose the relays properly and enable settings correctly. Private Replay or Tor Relays – normally not easily visible until unless someone tell you. You can also host own private relay not opened to internet of archive and back of your own notes. The technical landscape in nostr can be fast changing as more NIPs get proposed or updated. Relays admin can choose implement certain NIPs or not based on policy or technical limitations. Example NIP33 defines “long notes” aka blogs as you now reading this in habla site which #1 UI and site for "Editable" long notes – some relays donot implement or allow this. NIP07 is used for client authentication like nos2x and is implemented by all relays in fact. Nostr is so fasting changing-hence many links many broken Pushing long note again. To be continued again ... reference pics will added later also Hope this help you understand "why when what" to tune and maintain active set of proper relays. Relay Proxy, Relay aggregator or Relay multiplexer – Paid, Public, Free, Private, Event, Relays That’s all for now n more later ... Thank you 🙏 ! ⚡️ https://getalby.com/p/captjack ⚡️ PV 💜 🤙 References: https://habla.news/relays https://relay.exchange/ https://relays.vercel.app/ https://nostr.info/relays/ https://nostrudel.ninja/#/relays Related Articles: https://thebitcoinmanual.com/articles/types-nostr-relays/ nostr:naddr1qqd5c6t8dp6xu6twvukkvctnwss92jfqvehhygzwdaehguszyrtp7w79k045gq80mtnpdxjuzl9t7vjxk52rv80f888y5xsd5mh55qcyqqq823cf39s98 https://habla.news/u/current@getcurrent.io/1694434022411 @ 472f440f:5669301e
2024-10-11 14:20:54As we sprint toward the 2024 US Presidential election the case for using bitcoin as an asset to store value for the long term has never been stronger. The insanity of the incumbent power structure is being laid bare and it is becoming impossible to ignore the headwinds that the Borg faces moving forward. Yesterday morning and earlier today it became clear that inflation is rearing its head again. Not ideal for the soft landing Jerome Powell and Yellen are signaling to the markets after the first Fed Funds rate cut in years. It seems like the yield curve predicted this earlier this week when it inverted after a temporary normalizing period after the Fed's rate cut. Futhermore, it is becoming glaringly obvious that running historically high fiscal deficits while interest rates were at multi-decade highs was a pretty bad idea. As James Lavish points out, the data from the CBO earlier this week shows that the US federal government is running a deficit that is 13% higher than it was last year. This is at a time when real wages are still depressed, inflation is still suffocating American consumers and the private sector job market for American citizens is cratering. Speaking of the job market, the numbers that came in yesterday were worse than expected: The effect of Hurricane Helene should certainly be taken into consideration when looking at this jobs miss. However, even with the miss we know that these numbers have been under reported for years to make the economy seem healthier than it actually is. Even with Helene's effect taken into consideration this print will likely be revised higher 3-6 months from now. All of this points to a breaking point. A breaking point for the economy and, more importantly, a breaking point for overall confidence in the US government and its ability to operate with any semblance of fiscal responsibility. The chart that Pierre Rochard shares in the tweet at the top of this letter is the only chart that matters for anyone attempting to gauge where we find ourselves on the path to bitcoin realizing its full potential. There is $133 TRILLION worth of value sitting in global bond markets. Bitcoin is a far superior asset to store one's wealth in. Bond markets are beholden to the whims of the actors who issue those bonds. In the case of the US Treasury market, the largest bond market in the world, the US government. And as we have pointed out above, the US government is recklessly irresponsible when it comes to issuing debt with a complete inability to pay it back on the long-term. Inflation is up, the jobs market is cratering for the native born Americans who actually pay taxes, and the push toward a multi-polar geopolitical landscape is becoming more pronounced by the day. All of this points to a long-term weakening in demand for US treasuries. The only way out of this mess is to overtly default on this debt or inflate it away. The latter will most certainly be the route that is taken, which positions bitcoin extremely well as people seek the confines of an asset that cannot be debased because it cannot be controlled by a central authority. The levels of sovereign debt in the world are staggering. Do not let the bitcoin price consolidation of the last six months lull you into a state of complacency. Even the results of the Presidential election won't have a material effect on these dynamics. Though, a Donald Trump presidency would certainly be preferable if you prefer to see relatively sane policy enacted that would provide you with time to find safety in bitcoin. But, in regards to this sovereign debt crisis, that is the only benefit you can hope for; more time to prepare. I'll leave you with some thoughts from Porter Stansberry: "We are about to see the final destruction of the American experiment. Every economist knows this (see below) is correct; but nobody is going to tell you about it. I’ll summarize in plan English: We are fucked. 1. Debt is growing much faster than GD and interest expense is growing much faster than debt; and the real growth in entitlement spending hasn’t even begun yet. 2. Progressive taxation means nobody will ever vote for less spending + the combined size of government employees and dependents, there’s no way for America’s actual taxpayers (about 20m people) to ever win an election, so the spending won’t stop growing and, ironically, inflation will make demands for more spending to grow. 3. Inflation undermines both economic growth and social cohesion. The purple hair man-women weirdos are only the beginning; what comes next is scapegoating jews, blacks, immigrants and a huge increase in violence/domestic terror. Get ready America. This election has nothing to do with what’s coming. And neither Trump nor Kamala can stop it. Our experiment in freedom and self-government died in 1971 (when all restraint on government spending was abandoned with the gold standard.) You can only live at the expense of your neighbor until he runs out of money. And that day is here." --- Final thought... I hope my tux still fits for this wedding. Enjoy your weekend, freaks.Use the code "TFTC" for 15% off
@ 472f440f:5669301e
2024-10-11 14:20:54As we sprint toward the 2024 US Presidential election the case for using bitcoin as an asset to store value for the long term has never been stronger. The insanity of the incumbent power structure is being laid bare and it is becoming impossible to ignore the headwinds that the Borg faces moving forward. Yesterday morning and earlier today it became clear that inflation is rearing its head again. Not ideal for the soft landing Jerome Powell and Yellen are signaling to the markets after the first Fed Funds rate cut in years. It seems like the yield curve predicted this earlier this week when it inverted after a temporary normalizing period after the Fed's rate cut. Futhermore, it is becoming glaringly obvious that running historically high fiscal deficits while interest rates were at multi-decade highs was a pretty bad idea. As James Lavish points out, the data from the CBO earlier this week shows that the US federal government is running a deficit that is 13% higher than it was last year. This is at a time when real wages are still depressed, inflation is still suffocating American consumers and the private sector job market for American citizens is cratering. Speaking of the job market, the numbers that came in yesterday were worse than expected: The effect of Hurricane Helene should certainly be taken into consideration when looking at this jobs miss. However, even with the miss we know that these numbers have been under reported for years to make the economy seem healthier than it actually is. Even with Helene's effect taken into consideration this print will likely be revised higher 3-6 months from now. All of this points to a breaking point. A breaking point for the economy and, more importantly, a breaking point for overall confidence in the US government and its ability to operate with any semblance of fiscal responsibility. The chart that Pierre Rochard shares in the tweet at the top of this letter is the only chart that matters for anyone attempting to gauge where we find ourselves on the path to bitcoin realizing its full potential. There is $133 TRILLION worth of value sitting in global bond markets. Bitcoin is a far superior asset to store one's wealth in. Bond markets are beholden to the whims of the actors who issue those bonds. In the case of the US Treasury market, the largest bond market in the world, the US government. And as we have pointed out above, the US government is recklessly irresponsible when it comes to issuing debt with a complete inability to pay it back on the long-term. Inflation is up, the jobs market is cratering for the native born Americans who actually pay taxes, and the push toward a multi-polar geopolitical landscape is becoming more pronounced by the day. All of this points to a long-term weakening in demand for US treasuries. The only way out of this mess is to overtly default on this debt or inflate it away. The latter will most certainly be the route that is taken, which positions bitcoin extremely well as people seek the confines of an asset that cannot be debased because it cannot be controlled by a central authority. The levels of sovereign debt in the world are staggering. Do not let the bitcoin price consolidation of the last six months lull you into a state of complacency. Even the results of the Presidential election won't have a material effect on these dynamics. Though, a Donald Trump presidency would certainly be preferable if you prefer to see relatively sane policy enacted that would provide you with time to find safety in bitcoin. But, in regards to this sovereign debt crisis, that is the only benefit you can hope for; more time to prepare. I'll leave you with some thoughts from Porter Stansberry: "We are about to see the final destruction of the American experiment. Every economist knows this (see below) is correct; but nobody is going to tell you about it. I’ll summarize in plan English: We are fucked. 1. Debt is growing much faster than GD and interest expense is growing much faster than debt; and the real growth in entitlement spending hasn’t even begun yet. 2. Progressive taxation means nobody will ever vote for less spending + the combined size of government employees and dependents, there’s no way for America’s actual taxpayers (about 20m people) to ever win an election, so the spending won’t stop growing and, ironically, inflation will make demands for more spending to grow. 3. Inflation undermines both economic growth and social cohesion. The purple hair man-women weirdos are only the beginning; what comes next is scapegoating jews, blacks, immigrants and a huge increase in violence/domestic terror. Get ready America. This election has nothing to do with what’s coming. And neither Trump nor Kamala can stop it. Our experiment in freedom and self-government died in 1971 (when all restraint on government spending was abandoned with the gold standard.) You can only live at the expense of your neighbor until he runs out of money. And that day is here." --- Final thought... I hope my tux still fits for this wedding. Enjoy your weekend, freaks.Use the code "TFTC" for 15% off @ e88a691e:27850411
2024-10-11 13:17:16# An opinionated guide to Sauna. By NVK [🌐](https://primal.net/nvk) [🐦](https://twitter.com/nvk) ## Introduction Updated from the Sauna, October 7th 2024 After years of experimenting with different sauna types, I’ve developed strong opinions on the subject. The purpose of this article is to share these opinions with anyone who is interested in them and, hopefully, help others get more out of their sauna experience. I’m certain my opinions will offend some, including all the people who (in my view) are doing it wrong. I know that saunas are important to many cultures around the world and that my strongly held opinions may offend some of those cultures. Mind you, although I grew up in South America, I do have a fair amount of slavic blood in me. When I was a child, my grandfather regularly took me with him to the shvitz. One of my fondest memories from this time was the “Scottish Bath”, which involves standing against the sauna wall, execution-style, so that someone can spray you with freezing water from a high pressure hose. I’ve never heard of this outside of South American and can’t attest to whether it has any real Scottish origins. The various health claims about using a sauna are beyond the scope of this article. All I have to say is that, like many things in my life, like Bitcoin, the meat/keto diet, and fasting, I find sauna to be yet another cheat code to life: it’s a simple thing that just makes life a lot better. If you want a good primer on scientific health benefits of sauna, I recommend starting with [this article by Rhonda Patric](https://www.foundmyfitness.com/topics/sauna). She goes in depth. To be clear, it should go without saying that I am not a medical expert or professional. None of the opinions below are, or should be interpreted as, medical advice. There are many people for whom sauna use is not recommended. It would be prudent for any sauna user to consult with his or her doctor before entering a sauna. _Thanks to S. for taking the time to do a very helpful first review of this article. And thanks to The Wife for helping make my words legible and helping me make time to sauna–I don’t know which sacrifice was bigger._ ## Banya or Nothing When I talk about saunas, I’m talking about a sauna with a stove, either wood or electric, that allows for steam. I call this “Banya style”. To be clear, I’m distinguishing between saunas and steam baths. Steam baths have their own place, but they aren’t my thing and I don’t consider them saunas. A breakdown of the main types of saunas may be helpful, so you know which to avoid: 1. Wet saunas, which are typically cedar rooms with wood burning or electric stoves onto which you throw liquid to create steam (I call this “Banya style”); 2. Dry saunas, which are typically cedar rooms with wood burning or electric stoves without added steam (like Korean style saunas); and 3. Infrared saunas, which, unlike traditional saunas, don’t heat the surrounding air. Instead, they use infrared panels to warm your body directly. In my opinion, it’s Banya style or nothing. I’m not a huge fan of dry saunas, and I don’t even bother with infrared saunas. Infrared is a fiat-shitcoin. I want steam! ## How to Sauna ### Sauna Etiquette If you read no other part of this already-too-long-article, read this. Saunas are social places. There are proper ways of being in a sauna with others, and there are ways to do it wrong. You don’t want to be the person who ruins it for everyone. Here are some important etiquette tips: **Silence vs. Chatting:** It’s not a question of whether you have to stay silent in a sauna or if it’s ok to talk. It depends on the circumstances and who else is around. If you’re using a sauna that isn’t your own, ask the staff about the preferred custom. The noise level in a sauna differs depending on the group in the sauna at a particular time. If you do want to chat with others, there’s nothing wrong with that. But, pay attention to whether there are others in the sauna who'd prefer it quiet. And definitely do NOT be obnoxiously loud – yes, I’m looking at you bachelor(ette) group who just discovered the Russian Banya. **Coming and Going:** People rotate in and out of the sauna at different paces, so there will be people coming and going during your shvitz. But there are ways to come and go that are considerate and proper. Keep the f-ing door closed (which was the working title of this article). Once you leave, don’t come back inside moments later. Doing so disturbs your fellow sauna users, lets out the all-important steam, and prevents the sauna from reaching an appropriate temperature. If you’re in the sauna with a group of friends, try to coordinate your comings and goings so you’re all on the same cycle. If you can only last 5 min at a sauna, don’t go in too often at the risk of ruining it for others (assuming it’s not your own private sauna). Be fast when closing the sauna door when you come or leave. Otherwise, you will get dirty looks from others and may even hear mumbles of “quick quick, fast fast” from a Gray Beard. And you will deserve it. Never open the door right after someone puts water on the stove to make steam. It’s all about the steam. Don’t waste it. **Controlling the heat:** if you can’t handle the heat in the sauna, don’t just turn the heat down, because it ruins it for others. Instead, go to a lower bench or get out and take your break. Saunas are meant to be hot. That’s the whole point. **Personal Hygiene:** Shower before you go into the sauna. Don’t wear perfume, smelly deodorant, or fragrant lotions. Smells get amplified in a sauna. Have a towel under you, don't leave your drippings behind. Best yet, make a Z with your towel, this covers your butt and down under your feet. **Clothing:** sauna is not a place for wearing clothing. It is a place to get back to nature. If you are shy, just wrap a towel around yourself. People ask if I don't feel awkward, the answer is no. Who cares, humans naked is not novel. In many countries, it is strictly forbidden to wear clothing or bring anything but a towel into the sauna. It's understandable that may not be possible in North American public saunas on mix gender "family" days. If you have to wear something, then wear something 100% cotton or marino wool. You don't want plastic being backed into your genitals. One more thing, leave the watch out as it gets hot and will burn you. Also, flip-flops/sandals, stay outside. Some saunas sell body scrubs and masks for you to apply before or in the sauna. Note that once in the heat, these can get goopy and drippy and may melt into your eyes and mouth. So (in this opinionated guides’ wife’s opinion), they are better in theory than reality. **Adding Oils and scents:** As discussed below, it can be nice to add certain oils and other scents to the steam. But if there are others in the sauna, ask first before you do. **Where and how to sit:** Hot air rises. So, the higher benches are hotter and the lower benches are cooler. If you are a newbie, pick a lower bench so you don’t have to leave as quickly and open the door unnecessarily. It’s great to lay down in the sauna, but if it gets crowded, sit up to make room for others. When moving around to find your seat, don’t walk on the benches in your sandals. Leave your sandals outside the sauna or on the sauna floor. ### Sauna Temperature In most proper Russian style Banyas you will find temperatures of 80-95 degrees celsius, which, in my opinion, is the best range. Thats near your body. "Offical" on the dial will he 100-120C. But sometimes you want to take it a little easier or last a little longer in the sauna. In these cases, 65-85 at body, dial at 80-100. degrees celsius will do. However, if your sauna is below 85 degrees celsius on the dial, you might as well just go hide under your bed sheets and not waste your time. At some saunas in hotels, gyms, or spas, you may not be allowed to set the sauna as high as you’d like (see below). There are many tricks to circumvent these frustrating restrictions, but my legal counsel has advised me not to go into any details here. ### Sauna Duration The amount of time you spend in the sauna is a matter of personal preference and depends on the number of cycles you do (more on cycles, below). For your first round, my opinion is that most people should try to last 15 minutes in the sauna. If a sauna is at the proper temperature, most people will struggle to stay inside any longer. If you can stay inside for 20-30 minutes, your sauna is probably too cold and/or there is not enough steam. Many saunas have hourglasses inside to keep time, and I’ve never seen a sauna hourglass with more than 15 minutes, which should be a good hint. My preferred is; Cold Plunge => Sauna 15 min => Cold Plunge => Hydrate with Salt & Water, Rest 5-10min => Sauna 15min => Cold Plunge => Hydrate with Salt & Water, Rest 5-10min => Sauna 15min => Cold Plunge => Hydrate with Salt & Water, Rest if you can rest in the sun even better (no sunscreen poison please). You can add alcohol drinks to the hydration if you feel comfortable with that. But only add food after the last cycle. For subsequent rounds, hydration starts to play a bigger role in how long you stay inside. Most people seem to last longer on their first round than on their second or third. If you can do 15 minutes on your second round, great. But 5-10 minutes is also fine. ### Sauna Cycles The traditional Russian Banya method (and in this writer’s opinion, the best method) is to do sauna cycles. Go into the sauna and just stay as long as you can take it (up to 15 minutes or so). Then take a cold shower and/or cold plunge (see below). Then robe-up and go relax with water, tea or beer. Once you start feeling “normal” again, repeat. For me, three cycles is the sweet spot. I’ll do more cycles if I’m spending the day at the Banya facility. If I’m at home, where I often sauna every other day, I find just one or two cycles does the trick. Sometimes I add a cycle or two on the weekend. Occasionally, I like to go into the sauna as it’s warming up and before it reaches optimum heat (i.e. at around 60 degree celsius). This way, I can stay longer in the sauna for my first round (about 30-40 minutes). If I take this approach, I generally only do one more short round after my cold plunge. ### Cold showers and plunges In my experience, you want to take a cold shower or a cold plunge (or both, plunge is better) after the sauna cycle.After you come out of the sauna, immediately jump into cold plunge for a bit, i don't like to stay too long. Some Banya facilities will have a bucket filled with cold water that you can pull with a string to let the water pour over you, pull a couple times. The banyas may also have a cold pool of water into which you can plunge for a bit.  If I’m at my country place, after I get out of the sauna I jump into the cold lake. If it’s winter, I like to roll in the snow, which is satisfying. Some cultures would say that it’s not a real sauna experience unless you roll in at least one foot of snow. After your cold shower or plunge, put on a warm robe and go relax before going back into the sauna. I like to relax for 5-20 minutes, depending on how much time I have. This allows the body’s temperature to decrease slowly. I do not recommend going directly back into the sauna after your cold plunge. If you don’t give yourself enough time after the cold plunge, you will overheat and won’t last very long when you return to the sauna. ### Position There really are no rules here. The way you position yourself in the sauna depends on your mood and preference, and there are many options. For example, you can sauna seated with your legs hanging down or with your knees up. You can lie down if there’s room. My favorite position is to lie down on my back with my legs up against the wall and, assuming the ceiling is low enough, with my feet stretched against the ceiling. This is a great way to stretch the hamstrings (check out stretching under “Sauna Activities”, below). Choosing whether to sit on a higher bencher or lower bench is the best way to control the temperature you experience without adjusting the room temperature itself. You will notice the heat in the sauna increases exponentially every inch you go up. If you are struggling to stay in the sauna but don’t want to get out just yet, try moving down to a lower bench to last a little longer. Lying on the floor is the coolest spot and a great place for kids to start getting exposed to saunas. - - - #### There is no shame in going to lower benches or even the floor, there is only shame in opening the door before 15min - - - ### Getting Steamy Without steam, the sauna would just be a sad, hot oven (I’m looking at you, infrared sauna). The steam in the sauna has many benefits but most importantly it increases the thermal coupling of your body to the air and it feels great. The amount of steam in the sauna is a matter of personal taste. You don’t want to make it into a steam room (remember, steam rooms are NOT saunas). But, you do want the sauna to be very moist. I find that two to four ladles of water in a mid-size sauna every five to seven minutes does the trick. Keep it between 50-60% humidity. I keep a bucket of water in the sauna at all times so that I can continue to ladle water as I shvitz. Make sure to get a wood bucket and a metal ladle with a wooden handle. Wood ladles will crack, and if the handle is metal, it’ll burn you when you grab it. If, when you enter the sauna, it’s already been on for a while, the wood is likely to already be wet and the sauna full of steam, so you may not need to add too much water. However, if you’ve just turned on the sauna and the wood walls are dry, you will need to ladle more water to make the air moist enough. If the sauna is too moist for comfort, open the door and let it dry out a bit (obviously, only do this in a private sauna). Essential oils and even beer can all be added to the water to create scented steam. I recommend starting your sauna with just water, and add the scent as you get going. You can try all sorts of different essential oils. I’ve tried everything from oak and cedar to tangerine and cinnamon (gag) essential oil. In the end, there are really only two oils that are worth it, in my opinion. The first is eucalyptus. I’ve experimented with different types of eucalyptus oil, and the variety you use makes a difference. My favorite is eucalyptus globulus. I also like diluted pine tar oil. When you settle on your essential oil, add a healthy dose of the oil to the ladle filled with water. Never put the oil onto the oven directly. It’ll just burn. In a few Russian facilities, I’ve seen Gray Beards pour Russian beer onto the oven and it was actually quite nice. It’s almost like being in a cozy bakery while you sweat Some people like to place a salt brick or compressed solid blocks in their sauna from time to time. Put the salt block on the stove and pour water over it. The steam takes on a saltiness that feels nice. If a salt block is not available, you can get a cast iron teapot, fill it up with salt water, and place it on top of the stove. And for my most important steam tip, I recommend using the “towel spin”. This is an effective and underrated technique to help circulate steam in the sauna. After creating steam, take your towel above your head and spin it around hard, like a ceiling fan. This movement works like a convection oven and spreads and equalizes the heat and steam throughout the room. It might make the folks sitting lower down in the sauna a little hotter, but that's what they’re there for, isn’t it? ### Hydration Being hydrated is important to having a positive sauna experience. You will lose a lot of your body’s water in the sauna. Ideally, start to hydrate well up to an hour before your sauna. I like to add a pinch of salt to my water to encourage water retention. Do not bring any drinks into the sauna (the exception being a dedicated steam-beer, see above). Have your water or beverage when you’re outside the sauna, resting. If you find you need to drink water inside the sauna in order to cool yourself down, then it’s time for you to get out and allow your body a cool-down. When you’re outside the sauna, don’t immediately down a glass of super cold water because you will cool down your internal body too fast. Personally, I like to drink warm tea after my first two cycles. After my second cycle, I enjoy a beer (pre-keto days), soup, or vodka drink. When non-keto, I do enjoy adult drinks in the cycles. If you are doing a sauna while on a multi-day fast, you need to have water and salt, at a minimum. Otherwise, you will deplete your natural reserve of electrolytes and not be able to think straight. ### Sauna Frequency When it comes to frequency, if you are not in the equatorial heat do it every day. I now do mornings and end of day if I can. so 2x 2-3x cycles. In the summer, living in a hot & humid location, I sauna a lot less frequently. My desire to sauna is greatly diminished because I spend a lot of time in the sun and heat. ### What to wear **Sauna Hat:** I highly recommend wearing a Russian/Finish style wool hat when you’re inside the sauna. It may seem counterintuitive, but wearing a hat keeps your head cooler. An overheated head is not good for your brain. Wearing the hat stops you from overheating and lets you stay longer in the sauna. The temperature in a sauna is significantly hotter the higher in the room you are, and one’s head is at the top of the body (for most people). So protect your brain in style with a felt sauna hat. If you don’t have a felt sauna hat, buy one. They are easily found online. But in the meantime, you can wrap a dry towel around your head. Don’t forget to take your sauna hat off as you relax between cycles so your head can cool down.  **Clothing:** These days, many public saunas will have family days, men-only days, and women-only days. For obvious reasons, you’re only allowed to sauna naked if you’re attending one of the single-sex days. If you’re at home, there’s no good reason to wear shorts or a bathing suit. Sauna naked. It's a lot more pleasant. If you do wear clothing in the sauna, be careful with items with materials like metal or plastic attached. Things like pins, buttons, or string-ends will get very hot and probably burn you. Remember to take off any heat-conductive jewelry and leave your smart watch outside, as the heat will ruin its battery. Don’t wear your robe inside the sauna. A robe is what you wear outside when relaxing or eating. If you wear it inside, you’ll overheat (and look like an idiot). Go ahead and sweat out that body shame robe-free. You can bring a towel into the sauna to sit on, if you want. Shoes or sandals are highly recommended in public facilities. I mean, there are many people walking around wet. Ew. But keep your sandals outside the sauna itself, or on the sauna floor. ### Sauna activities. Don’t overthink it. Sitting in a sauna is activity enough, in my opinion. But there are some sauna activities you can do: **Veniks/Viht beating:** these are bundles of leaves (commonly birch, oak, or eucalyptus) that are pre-soaked in hot water. Someone with both strength and capacity to exert themselves in the heat will beat your whole body with the leaves. This exfoliates your skin and also gets the plant oils to permeate your skin. And it’s very relaxing. If you’re at a sauna facility, don’t just grab any bundle you see lying around - that belongs to someone else and veniks aren’t shared. You have to bring your own or buy them at the front desk. **Stretching:** this is a great activity to do in the sauna, but make sure to go very easy. Your muscles will be super warm and you don’t want to overdo it and hurt yourself. **Exercise or Sex:** your heart better be in good shape if you try out these high intensity activities in the sauna. If you engage in the latter, you better be in your own home sauna. With respect to the former, I think doing some leg-ups can be very satisfying. **Phone use:** If you’re at home, it’s nice to use your sauna time to shit-post on Twitter or read an article, if you feel like it. Just keep your phone close to the colder, lower parts near the floor or it’ll overheat and shut down. You can also place the phone outside of the air vent and play a [podcast! The Bitcoin.review is great ;)](https://bitcoin.review) **Napping:** I don’t recommend this. If you fall asleep or pass out, you will probably die due to overheating or dehydration. **Chatting:** Saunas are great places for conversations (subject to the caveats I address above). Note that nowadays, microphone modules are both very tiny and can withstand high temperatures, so it’s no longer recommended to reenact mafia movie sauna scenes. **Eating and Drinking:** As discussed above, never have food or drink inside the sauna. But when you finish your sauna, take advantage of whatever snacks the facility offers. For Russian joints, the soups, fish roe and dry salty fish snacks are great. Again, don’t eat before your sauna; wait until you’re done. Some places will have bottled salty-ish lake water, and beer seems to be a good source of salts and re-hydration. Vodka drinks are nice sometimes, too. My favorites are vodka with beet juice and horseradish, vodka with pickle juice, or just a chilled shot of Zubrowka (vodka infused with bison grass). Teas are also very enjoyable post-sauna. I prefer non-caffeinated berry teas. Some Banyas even offer free tea to patrons.  ## Ready to Sweat It Out? Thanks to this fantastic guide to sauna, you’re now feeling confident and excited to seek out a solid sauna. So where do you go? ## Where to Find a Sauna **Spas:** Spas are not the best place to have an optimal sauna experience. Saunas at spas are typically not hot enough and spas have annoying staff whose job it is to enforce idiotic rules and practices that prevent you from having a real sauna experience. **Gyms & Hotels:** These are some of the worst places to sauna. For liability reasons, these saunas tend to be too cold and there are often mechanisms that prevent you from raising the temperature. Here, you’ll often see saunas with glass doors, which may look chic, but are inefficient and stupid because they don’t seal properly and leak steam. Gyms and hotels are high traffic areas, so people who don’t know what they are doing are constantly coming and going from the sauna, which, as we discussed, is a sauna no-no. If you still want to try the sauna at your gym or hotel, I recommend going in naked. It’ll deter people from joining you and ruining the little steam you managed to get going. **Traditional bath houses (Banyas):** These usually offer a great experience because they deliver a super hot sauna, good cold baths and plunges, delicious food and drinks, and knowledgeable staff. **Home:** Yes, you can build a great sauna in your own home! You can create a small space in your basement, turn a closet or cold room into a sauna, or just add an outdoor hut or barrel sauna in your backyard. This is the best way for you to control the whole experience and do it often. As with anything, the easier it is to access, the more you will do it. _Build it. They will Come_ Many people have asked me for details about sauna building. If you’re ready to build your own personal home sauna, here are some important considerations. #### Materials Saunas are insulated rooms, most commonly finished with cedar tung and groove slats. Cedar is used because it doesn’t rot with moisture. You don’t want treated wood as it will release all the bad stuff that keeps the wood from rotting into the air when heated. Cedar interior is often placed over a vapor barrier, followed by insulation and then the outer wall. Many outdoor saunas are not insulated. They simply have a single layer of cedar 2x6 planks functioning as both the interior and exterior. Non-insulated saunas need much more heating power in the winter. #### Structure For indoor saunas, you may want to find a bricklayer to build something for you. Traditional facilities often have brick-lined rooms and very large wood-burning stoves. You can buy prefab outdoor saunas, which are often sheds or barrels. After experimenting with both, I’ve concluded that barrel saunas are inferior, even though that’s what I have at my country property. This is because barrels have concave ceilings and inner walls. This means the benches are lower and the curve makes the topmost part of the ceiling (and the hottest part) the furthest from you, or inaccessible. The spinning towel trick really helps in the barrel. When it comes to buying a sauna, go with the most traditional structure possible. They are based on thousands of years of evolution and knowledge. Portable tent saunas are fun, but impractical because you have to set them up before each use. Bench height inside the sauna is important. I think the top-most bench should be very near the ceiling. This way, when you’re lying down, you can use the ceiling to stretch the hamstrings. As a rule of thumb, bench length should allow you to lie down completely. It is also nice to have at least one lower bench for visitors or less intense sauna days.  #### Sauna Ovens There are two main types of sauna ovens: wood burning and electrical (with gas heating being available, but not common). If the location you are building allows for it, go with electrical. It’s practical and easy to get going quickly. This means you will use it more often. Wood burning saunas are romantic and smell great, but it is a lot more work to get a fire going, especially in the winter. Opt for oven sizes that are recommended or above recommended for the size of the sauna. A larger oven means more thermic inertia, more rocks for steam, and therefore less time to warm up the room. Bigger is better. The Scandinavians make the best quality ovens. #### Oven controllers There are two types of temperature control devices: the analog cooking-style or the digital type. I think, due to liability and safety, all ovens have a timer that max out at one hour. The digital oven controllers are fantastic and I have one in the city in my basement sauna. However, you have to consider your environment. For me, temperatures in the winter can reach below -30C and in the summer, over 40C. This massive range can take a toll on outdoor equipment and materials. For this reason, I opted for an analog controller for my outdoor sauna in the country, since the weather will likely ruin the electronics of the digital controller. I would avoid ovens with analog pre-heat timers. They are great in theory, but the implementation is utter garbage. The timer won’t be precise and it’ll just lead to frustration, for example, when you thought you set the oven to start in three hours, but it actually started in two hours and already turned off. #### Important Sauna Gear Windows are nice to have, especially if you have a view to enjoy. Opt for at least a cedar door with a little window. Do not go with modern glass door styles. They are crap. They have gaps, no insulation, and let in too much light. Saunas need thermometers and hygrometers (to measure humidity). The thermometers should be rated for saunas and be visible inside. This is both for safety and bragging rights. I think having an hourglass inside your sauna is a must. Being able to know for sure how long you’ve been inside is important, since your sense of timing inside the sauna may be off depending on the state of your mind and body on a given day. You shouldn’t wear a watch inside the sauna, since it’ll overheat or break. Having a clock visible from the inside is also a good idea, especially if you sauna often and have a wife and kids who you don’t want to leave you. Air circulation is an often-overlooked but important part of a sauna design. Saunas should not have stale air. The best sauna design creates natural “real convection” by placing an air intake under the oven wall and another at the top opposite wall. This allows fresh air to enter the sauna while in use. Be sure to add regulators, since you don’t want to cool the sauna or expel all steam. Without regulators you may get too much or too little air in. With too much air, you may cool the sauna down too much and/or lose too much steam. #### Nice Things to Have Lights are optional but welcome additions. It can be unpleasant to have no lighting at all, especially in an outdoor sauna on a cold, dark night. Lights should be warm-temperature and low power. I recommend an oven light, since they don’t sweat the heat (get it?) and are often low power. Put a baking tray under your oven–thank me later. Wood “pillows” for your head are nice and don’t get sweat-stained and stinky, like a fabric pillow. Keep some extra felt hats near your sauna so when you or your guests forget their hat, you still have easy access to one. I like to keep a couple of essential oils on the floor of the sauna, for easy access. If you keep the oils too high in the sauna, they’ll get too hot and spoil. I place some duck boards over floor tiles in the sauna to prevent cold feet. I also like to keep a small, natural broom inside the sauna to sweep up any dirt or leaves that come into the sauna on people’s feet. ## Final words As you can tell, I have some strong opinions when it comes to the proper way to enjoy a sauna. My hope is that my musings will help you to maximize your own sauna experience.. If you follow this guide, I’m certain you will benefit from and enjoy the sauna as much as I do and, just maybe, you too will develop your own strongly held opinions that will most definitely offend me. ### Thanks for reading, please close the F-ing door. ps, you can get a Bitcoin Honey Badger Sauna Hat [here](https://store.coinkite.com/store/ht-sauna) - EOF
@ e88a691e:27850411
2024-10-11 13:17:16# An opinionated guide to Sauna. By NVK [🌐](https://primal.net/nvk) [🐦](https://twitter.com/nvk) ## Introduction Updated from the Sauna, October 7th 2024 After years of experimenting with different sauna types, I’ve developed strong opinions on the subject. The purpose of this article is to share these opinions with anyone who is interested in them and, hopefully, help others get more out of their sauna experience. I’m certain my opinions will offend some, including all the people who (in my view) are doing it wrong. I know that saunas are important to many cultures around the world and that my strongly held opinions may offend some of those cultures. Mind you, although I grew up in South America, I do have a fair amount of slavic blood in me. When I was a child, my grandfather regularly took me with him to the shvitz. One of my fondest memories from this time was the “Scottish Bath”, which involves standing against the sauna wall, execution-style, so that someone can spray you with freezing water from a high pressure hose. I’ve never heard of this outside of South American and can’t attest to whether it has any real Scottish origins. The various health claims about using a sauna are beyond the scope of this article. All I have to say is that, like many things in my life, like Bitcoin, the meat/keto diet, and fasting, I find sauna to be yet another cheat code to life: it’s a simple thing that just makes life a lot better. If you want a good primer on scientific health benefits of sauna, I recommend starting with [this article by Rhonda Patric](https://www.foundmyfitness.com/topics/sauna). She goes in depth. To be clear, it should go without saying that I am not a medical expert or professional. None of the opinions below are, or should be interpreted as, medical advice. There are many people for whom sauna use is not recommended. It would be prudent for any sauna user to consult with his or her doctor before entering a sauna. _Thanks to S. for taking the time to do a very helpful first review of this article. And thanks to The Wife for helping make my words legible and helping me make time to sauna–I don’t know which sacrifice was bigger._ ## Banya or Nothing When I talk about saunas, I’m talking about a sauna with a stove, either wood or electric, that allows for steam. I call this “Banya style”. To be clear, I’m distinguishing between saunas and steam baths. Steam baths have their own place, but they aren’t my thing and I don’t consider them saunas. A breakdown of the main types of saunas may be helpful, so you know which to avoid: 1. Wet saunas, which are typically cedar rooms with wood burning or electric stoves onto which you throw liquid to create steam (I call this “Banya style”); 2. Dry saunas, which are typically cedar rooms with wood burning or electric stoves without added steam (like Korean style saunas); and 3. Infrared saunas, which, unlike traditional saunas, don’t heat the surrounding air. Instead, they use infrared panels to warm your body directly. In my opinion, it’s Banya style or nothing. I’m not a huge fan of dry saunas, and I don’t even bother with infrared saunas. Infrared is a fiat-shitcoin. I want steam! ## How to Sauna ### Sauna Etiquette If you read no other part of this already-too-long-article, read this. Saunas are social places. There are proper ways of being in a sauna with others, and there are ways to do it wrong. You don’t want to be the person who ruins it for everyone. Here are some important etiquette tips: **Silence vs. Chatting:** It’s not a question of whether you have to stay silent in a sauna or if it’s ok to talk. It depends on the circumstances and who else is around. If you’re using a sauna that isn’t your own, ask the staff about the preferred custom. The noise level in a sauna differs depending on the group in the sauna at a particular time. If you do want to chat with others, there’s nothing wrong with that. But, pay attention to whether there are others in the sauna who'd prefer it quiet. And definitely do NOT be obnoxiously loud – yes, I’m looking at you bachelor(ette) group who just discovered the Russian Banya. **Coming and Going:** People rotate in and out of the sauna at different paces, so there will be people coming and going during your shvitz. But there are ways to come and go that are considerate and proper. Keep the f-ing door closed (which was the working title of this article). Once you leave, don’t come back inside moments later. Doing so disturbs your fellow sauna users, lets out the all-important steam, and prevents the sauna from reaching an appropriate temperature. If you’re in the sauna with a group of friends, try to coordinate your comings and goings so you’re all on the same cycle. If you can only last 5 min at a sauna, don’t go in too often at the risk of ruining it for others (assuming it’s not your own private sauna). Be fast when closing the sauna door when you come or leave. Otherwise, you will get dirty looks from others and may even hear mumbles of “quick quick, fast fast” from a Gray Beard. And you will deserve it. Never open the door right after someone puts water on the stove to make steam. It’s all about the steam. Don’t waste it. **Controlling the heat:** if you can’t handle the heat in the sauna, don’t just turn the heat down, because it ruins it for others. Instead, go to a lower bench or get out and take your break. Saunas are meant to be hot. That’s the whole point. **Personal Hygiene:** Shower before you go into the sauna. Don’t wear perfume, smelly deodorant, or fragrant lotions. Smells get amplified in a sauna. Have a towel under you, don't leave your drippings behind. Best yet, make a Z with your towel, this covers your butt and down under your feet. **Clothing:** sauna is not a place for wearing clothing. It is a place to get back to nature. If you are shy, just wrap a towel around yourself. People ask if I don't feel awkward, the answer is no. Who cares, humans naked is not novel. In many countries, it is strictly forbidden to wear clothing or bring anything but a towel into the sauna. It's understandable that may not be possible in North American public saunas on mix gender "family" days. If you have to wear something, then wear something 100% cotton or marino wool. You don't want plastic being backed into your genitals. One more thing, leave the watch out as it gets hot and will burn you. Also, flip-flops/sandals, stay outside. Some saunas sell body scrubs and masks for you to apply before or in the sauna. Note that once in the heat, these can get goopy and drippy and may melt into your eyes and mouth. So (in this opinionated guides’ wife’s opinion), they are better in theory than reality. **Adding Oils and scents:** As discussed below, it can be nice to add certain oils and other scents to the steam. But if there are others in the sauna, ask first before you do. **Where and how to sit:** Hot air rises. So, the higher benches are hotter and the lower benches are cooler. If you are a newbie, pick a lower bench so you don’t have to leave as quickly and open the door unnecessarily. It’s great to lay down in the sauna, but if it gets crowded, sit up to make room for others. When moving around to find your seat, don’t walk on the benches in your sandals. Leave your sandals outside the sauna or on the sauna floor. ### Sauna Temperature In most proper Russian style Banyas you will find temperatures of 80-95 degrees celsius, which, in my opinion, is the best range. Thats near your body. "Offical" on the dial will he 100-120C. But sometimes you want to take it a little easier or last a little longer in the sauna. In these cases, 65-85 at body, dial at 80-100. degrees celsius will do. However, if your sauna is below 85 degrees celsius on the dial, you might as well just go hide under your bed sheets and not waste your time. At some saunas in hotels, gyms, or spas, you may not be allowed to set the sauna as high as you’d like (see below). There are many tricks to circumvent these frustrating restrictions, but my legal counsel has advised me not to go into any details here. ### Sauna Duration The amount of time you spend in the sauna is a matter of personal preference and depends on the number of cycles you do (more on cycles, below). For your first round, my opinion is that most people should try to last 15 minutes in the sauna. If a sauna is at the proper temperature, most people will struggle to stay inside any longer. If you can stay inside for 20-30 minutes, your sauna is probably too cold and/or there is not enough steam. Many saunas have hourglasses inside to keep time, and I’ve never seen a sauna hourglass with more than 15 minutes, which should be a good hint. My preferred is; Cold Plunge => Sauna 15 min => Cold Plunge => Hydrate with Salt & Water, Rest 5-10min => Sauna 15min => Cold Plunge => Hydrate with Salt & Water, Rest 5-10min => Sauna 15min => Cold Plunge => Hydrate with Salt & Water, Rest if you can rest in the sun even better (no sunscreen poison please). You can add alcohol drinks to the hydration if you feel comfortable with that. But only add food after the last cycle. For subsequent rounds, hydration starts to play a bigger role in how long you stay inside. Most people seem to last longer on their first round than on their second or third. If you can do 15 minutes on your second round, great. But 5-10 minutes is also fine. ### Sauna Cycles The traditional Russian Banya method (and in this writer’s opinion, the best method) is to do sauna cycles. Go into the sauna and just stay as long as you can take it (up to 15 minutes or so). Then take a cold shower and/or cold plunge (see below). Then robe-up and go relax with water, tea or beer. Once you start feeling “normal” again, repeat. For me, three cycles is the sweet spot. I’ll do more cycles if I’m spending the day at the Banya facility. If I’m at home, where I often sauna every other day, I find just one or two cycles does the trick. Sometimes I add a cycle or two on the weekend. Occasionally, I like to go into the sauna as it’s warming up and before it reaches optimum heat (i.e. at around 60 degree celsius). This way, I can stay longer in the sauna for my first round (about 30-40 minutes). If I take this approach, I generally only do one more short round after my cold plunge. ### Cold showers and plunges In my experience, you want to take a cold shower or a cold plunge (or both, plunge is better) after the sauna cycle.After you come out of the sauna, immediately jump into cold plunge for a bit, i don't like to stay too long. Some Banya facilities will have a bucket filled with cold water that you can pull with a string to let the water pour over you, pull a couple times. The banyas may also have a cold pool of water into which you can plunge for a bit.  If I’m at my country place, after I get out of the sauna I jump into the cold lake. If it’s winter, I like to roll in the snow, which is satisfying. Some cultures would say that it’s not a real sauna experience unless you roll in at least one foot of snow. After your cold shower or plunge, put on a warm robe and go relax before going back into the sauna. I like to relax for 5-20 minutes, depending on how much time I have. This allows the body’s temperature to decrease slowly. I do not recommend going directly back into the sauna after your cold plunge. If you don’t give yourself enough time after the cold plunge, you will overheat and won’t last very long when you return to the sauna. ### Position There really are no rules here. The way you position yourself in the sauna depends on your mood and preference, and there are many options. For example, you can sauna seated with your legs hanging down or with your knees up. You can lie down if there’s room. My favorite position is to lie down on my back with my legs up against the wall and, assuming the ceiling is low enough, with my feet stretched against the ceiling. This is a great way to stretch the hamstrings (check out stretching under “Sauna Activities”, below). Choosing whether to sit on a higher bencher or lower bench is the best way to control the temperature you experience without adjusting the room temperature itself. You will notice the heat in the sauna increases exponentially every inch you go up. If you are struggling to stay in the sauna but don’t want to get out just yet, try moving down to a lower bench to last a little longer. Lying on the floor is the coolest spot and a great place for kids to start getting exposed to saunas. - - - #### There is no shame in going to lower benches or even the floor, there is only shame in opening the door before 15min - - - ### Getting Steamy Without steam, the sauna would just be a sad, hot oven (I’m looking at you, infrared sauna). The steam in the sauna has many benefits but most importantly it increases the thermal coupling of your body to the air and it feels great. The amount of steam in the sauna is a matter of personal taste. You don’t want to make it into a steam room (remember, steam rooms are NOT saunas). But, you do want the sauna to be very moist. I find that two to four ladles of water in a mid-size sauna every five to seven minutes does the trick. Keep it between 50-60% humidity. I keep a bucket of water in the sauna at all times so that I can continue to ladle water as I shvitz. Make sure to get a wood bucket and a metal ladle with a wooden handle. Wood ladles will crack, and if the handle is metal, it’ll burn you when you grab it. If, when you enter the sauna, it’s already been on for a while, the wood is likely to already be wet and the sauna full of steam, so you may not need to add too much water. However, if you’ve just turned on the sauna and the wood walls are dry, you will need to ladle more water to make the air moist enough. If the sauna is too moist for comfort, open the door and let it dry out a bit (obviously, only do this in a private sauna). Essential oils and even beer can all be added to the water to create scented steam. I recommend starting your sauna with just water, and add the scent as you get going. You can try all sorts of different essential oils. I’ve tried everything from oak and cedar to tangerine and cinnamon (gag) essential oil. In the end, there are really only two oils that are worth it, in my opinion. The first is eucalyptus. I’ve experimented with different types of eucalyptus oil, and the variety you use makes a difference. My favorite is eucalyptus globulus. I also like diluted pine tar oil. When you settle on your essential oil, add a healthy dose of the oil to the ladle filled with water. Never put the oil onto the oven directly. It’ll just burn. In a few Russian facilities, I’ve seen Gray Beards pour Russian beer onto the oven and it was actually quite nice. It’s almost like being in a cozy bakery while you sweat Some people like to place a salt brick or compressed solid blocks in their sauna from time to time. Put the salt block on the stove and pour water over it. The steam takes on a saltiness that feels nice. If a salt block is not available, you can get a cast iron teapot, fill it up with salt water, and place it on top of the stove. And for my most important steam tip, I recommend using the “towel spin”. This is an effective and underrated technique to help circulate steam in the sauna. After creating steam, take your towel above your head and spin it around hard, like a ceiling fan. This movement works like a convection oven and spreads and equalizes the heat and steam throughout the room. It might make the folks sitting lower down in the sauna a little hotter, but that's what they’re there for, isn’t it? ### Hydration Being hydrated is important to having a positive sauna experience. You will lose a lot of your body’s water in the sauna. Ideally, start to hydrate well up to an hour before your sauna. I like to add a pinch of salt to my water to encourage water retention. Do not bring any drinks into the sauna (the exception being a dedicated steam-beer, see above). Have your water or beverage when you’re outside the sauna, resting. If you find you need to drink water inside the sauna in order to cool yourself down, then it’s time for you to get out and allow your body a cool-down. When you’re outside the sauna, don’t immediately down a glass of super cold water because you will cool down your internal body too fast. Personally, I like to drink warm tea after my first two cycles. After my second cycle, I enjoy a beer (pre-keto days), soup, or vodka drink. When non-keto, I do enjoy adult drinks in the cycles. If you are doing a sauna while on a multi-day fast, you need to have water and salt, at a minimum. Otherwise, you will deplete your natural reserve of electrolytes and not be able to think straight. ### Sauna Frequency When it comes to frequency, if you are not in the equatorial heat do it every day. I now do mornings and end of day if I can. so 2x 2-3x cycles. In the summer, living in a hot & humid location, I sauna a lot less frequently. My desire to sauna is greatly diminished because I spend a lot of time in the sun and heat. ### What to wear **Sauna Hat:** I highly recommend wearing a Russian/Finish style wool hat when you’re inside the sauna. It may seem counterintuitive, but wearing a hat keeps your head cooler. An overheated head is not good for your brain. Wearing the hat stops you from overheating and lets you stay longer in the sauna. The temperature in a sauna is significantly hotter the higher in the room you are, and one’s head is at the top of the body (for most people). So protect your brain in style with a felt sauna hat. If you don’t have a felt sauna hat, buy one. They are easily found online. But in the meantime, you can wrap a dry towel around your head. Don’t forget to take your sauna hat off as you relax between cycles so your head can cool down.  **Clothing:** These days, many public saunas will have family days, men-only days, and women-only days. For obvious reasons, you’re only allowed to sauna naked if you’re attending one of the single-sex days. If you’re at home, there’s no good reason to wear shorts or a bathing suit. Sauna naked. It's a lot more pleasant. If you do wear clothing in the sauna, be careful with items with materials like metal or plastic attached. Things like pins, buttons, or string-ends will get very hot and probably burn you. Remember to take off any heat-conductive jewelry and leave your smart watch outside, as the heat will ruin its battery. Don’t wear your robe inside the sauna. A robe is what you wear outside when relaxing or eating. If you wear it inside, you’ll overheat (and look like an idiot). Go ahead and sweat out that body shame robe-free. You can bring a towel into the sauna to sit on, if you want. Shoes or sandals are highly recommended in public facilities. I mean, there are many people walking around wet. Ew. But keep your sandals outside the sauna itself, or on the sauna floor. ### Sauna activities. Don’t overthink it. Sitting in a sauna is activity enough, in my opinion. But there are some sauna activities you can do: **Veniks/Viht beating:** these are bundles of leaves (commonly birch, oak, or eucalyptus) that are pre-soaked in hot water. Someone with both strength and capacity to exert themselves in the heat will beat your whole body with the leaves. This exfoliates your skin and also gets the plant oils to permeate your skin. And it’s very relaxing. If you’re at a sauna facility, don’t just grab any bundle you see lying around - that belongs to someone else and veniks aren’t shared. You have to bring your own or buy them at the front desk. **Stretching:** this is a great activity to do in the sauna, but make sure to go very easy. Your muscles will be super warm and you don’t want to overdo it and hurt yourself. **Exercise or Sex:** your heart better be in good shape if you try out these high intensity activities in the sauna. If you engage in the latter, you better be in your own home sauna. With respect to the former, I think doing some leg-ups can be very satisfying. **Phone use:** If you’re at home, it’s nice to use your sauna time to shit-post on Twitter or read an article, if you feel like it. Just keep your phone close to the colder, lower parts near the floor or it’ll overheat and shut down. You can also place the phone outside of the air vent and play a [podcast! The Bitcoin.review is great ;)](https://bitcoin.review) **Napping:** I don’t recommend this. If you fall asleep or pass out, you will probably die due to overheating or dehydration. **Chatting:** Saunas are great places for conversations (subject to the caveats I address above). Note that nowadays, microphone modules are both very tiny and can withstand high temperatures, so it’s no longer recommended to reenact mafia movie sauna scenes. **Eating and Drinking:** As discussed above, never have food or drink inside the sauna. But when you finish your sauna, take advantage of whatever snacks the facility offers. For Russian joints, the soups, fish roe and dry salty fish snacks are great. Again, don’t eat before your sauna; wait until you’re done. Some places will have bottled salty-ish lake water, and beer seems to be a good source of salts and re-hydration. Vodka drinks are nice sometimes, too. My favorites are vodka with beet juice and horseradish, vodka with pickle juice, or just a chilled shot of Zubrowka (vodka infused with bison grass). Teas are also very enjoyable post-sauna. I prefer non-caffeinated berry teas. Some Banyas even offer free tea to patrons.  ## Ready to Sweat It Out? Thanks to this fantastic guide to sauna, you’re now feeling confident and excited to seek out a solid sauna. So where do you go? ## Where to Find a Sauna **Spas:** Spas are not the best place to have an optimal sauna experience. Saunas at spas are typically not hot enough and spas have annoying staff whose job it is to enforce idiotic rules and practices that prevent you from having a real sauna experience. **Gyms & Hotels:** These are some of the worst places to sauna. For liability reasons, these saunas tend to be too cold and there are often mechanisms that prevent you from raising the temperature. Here, you’ll often see saunas with glass doors, which may look chic, but are inefficient and stupid because they don’t seal properly and leak steam. Gyms and hotels are high traffic areas, so people who don’t know what they are doing are constantly coming and going from the sauna, which, as we discussed, is a sauna no-no. If you still want to try the sauna at your gym or hotel, I recommend going in naked. It’ll deter people from joining you and ruining the little steam you managed to get going. **Traditional bath houses (Banyas):** These usually offer a great experience because they deliver a super hot sauna, good cold baths and plunges, delicious food and drinks, and knowledgeable staff. **Home:** Yes, you can build a great sauna in your own home! You can create a small space in your basement, turn a closet or cold room into a sauna, or just add an outdoor hut or barrel sauna in your backyard. This is the best way for you to control the whole experience and do it often. As with anything, the easier it is to access, the more you will do it. _Build it. They will Come_ Many people have asked me for details about sauna building. If you’re ready to build your own personal home sauna, here are some important considerations. #### Materials Saunas are insulated rooms, most commonly finished with cedar tung and groove slats. Cedar is used because it doesn’t rot with moisture. You don’t want treated wood as it will release all the bad stuff that keeps the wood from rotting into the air when heated. Cedar interior is often placed over a vapor barrier, followed by insulation and then the outer wall. Many outdoor saunas are not insulated. They simply have a single layer of cedar 2x6 planks functioning as both the interior and exterior. Non-insulated saunas need much more heating power in the winter. #### Structure For indoor saunas, you may want to find a bricklayer to build something for you. Traditional facilities often have brick-lined rooms and very large wood-burning stoves. You can buy prefab outdoor saunas, which are often sheds or barrels. After experimenting with both, I’ve concluded that barrel saunas are inferior, even though that’s what I have at my country property. This is because barrels have concave ceilings and inner walls. This means the benches are lower and the curve makes the topmost part of the ceiling (and the hottest part) the furthest from you, or inaccessible. The spinning towel trick really helps in the barrel. When it comes to buying a sauna, go with the most traditional structure possible. They are based on thousands of years of evolution and knowledge. Portable tent saunas are fun, but impractical because you have to set them up before each use. Bench height inside the sauna is important. I think the top-most bench should be very near the ceiling. This way, when you’re lying down, you can use the ceiling to stretch the hamstrings. As a rule of thumb, bench length should allow you to lie down completely. It is also nice to have at least one lower bench for visitors or less intense sauna days.  #### Sauna Ovens There are two main types of sauna ovens: wood burning and electrical (with gas heating being available, but not common). If the location you are building allows for it, go with electrical. It’s practical and easy to get going quickly. This means you will use it more often. Wood burning saunas are romantic and smell great, but it is a lot more work to get a fire going, especially in the winter. Opt for oven sizes that are recommended or above recommended for the size of the sauna. A larger oven means more thermic inertia, more rocks for steam, and therefore less time to warm up the room. Bigger is better. The Scandinavians make the best quality ovens. #### Oven controllers There are two types of temperature control devices: the analog cooking-style or the digital type. I think, due to liability and safety, all ovens have a timer that max out at one hour. The digital oven controllers are fantastic and I have one in the city in my basement sauna. However, you have to consider your environment. For me, temperatures in the winter can reach below -30C and in the summer, over 40C. This massive range can take a toll on outdoor equipment and materials. For this reason, I opted for an analog controller for my outdoor sauna in the country, since the weather will likely ruin the electronics of the digital controller. I would avoid ovens with analog pre-heat timers. They are great in theory, but the implementation is utter garbage. The timer won’t be precise and it’ll just lead to frustration, for example, when you thought you set the oven to start in three hours, but it actually started in two hours and already turned off. #### Important Sauna Gear Windows are nice to have, especially if you have a view to enjoy. Opt for at least a cedar door with a little window. Do not go with modern glass door styles. They are crap. They have gaps, no insulation, and let in too much light. Saunas need thermometers and hygrometers (to measure humidity). The thermometers should be rated for saunas and be visible inside. This is both for safety and bragging rights. I think having an hourglass inside your sauna is a must. Being able to know for sure how long you’ve been inside is important, since your sense of timing inside the sauna may be off depending on the state of your mind and body on a given day. You shouldn’t wear a watch inside the sauna, since it’ll overheat or break. Having a clock visible from the inside is also a good idea, especially if you sauna often and have a wife and kids who you don’t want to leave you. Air circulation is an often-overlooked but important part of a sauna design. Saunas should not have stale air. The best sauna design creates natural “real convection” by placing an air intake under the oven wall and another at the top opposite wall. This allows fresh air to enter the sauna while in use. Be sure to add regulators, since you don’t want to cool the sauna or expel all steam. Without regulators you may get too much or too little air in. With too much air, you may cool the sauna down too much and/or lose too much steam. #### Nice Things to Have Lights are optional but welcome additions. It can be unpleasant to have no lighting at all, especially in an outdoor sauna on a cold, dark night. Lights should be warm-temperature and low power. I recommend an oven light, since they don’t sweat the heat (get it?) and are often low power. Put a baking tray under your oven–thank me later. Wood “pillows” for your head are nice and don’t get sweat-stained and stinky, like a fabric pillow. Keep some extra felt hats near your sauna so when you or your guests forget their hat, you still have easy access to one. I like to keep a couple of essential oils on the floor of the sauna, for easy access. If you keep the oils too high in the sauna, they’ll get too hot and spoil. I place some duck boards over floor tiles in the sauna to prevent cold feet. I also like to keep a small, natural broom inside the sauna to sweep up any dirt or leaves that come into the sauna on people’s feet. ## Final words As you can tell, I have some strong opinions when it comes to the proper way to enjoy a sauna. My hope is that my musings will help you to maximize your own sauna experience.. If you follow this guide, I’m certain you will benefit from and enjoy the sauna as much as I do and, just maybe, you too will develop your own strongly held opinions that will most definitely offend me. ### Thanks for reading, please close the F-ing door. ps, you can get a Bitcoin Honey Badger Sauna Hat [here](https://store.coinkite.com/store/ht-sauna) - EOF @ eac63075:b4988b48
2024-10-10 18:12:38Companies like Meta (formerly Facebook) and Twitter (now X) control platforms that have become the main channels of communication for millions of people worldwide. At the center of this discussion are figures like Mark Zuckerberg and Elon Musk, whose recent actions raise serious questions about freedom of speech, censorship, and political manipulation. --- <https://fountain.fm/episode/VzJItfySZ8z6417prHyD> --- Recently, a public letter written by Mark Zuckerberg revealed how the U.S. government, under Joe Biden’s administration, pressured Facebook to censor information during the COVID-19 pandemic. The controversy involves, among other topics, the censorship of content related to Biden’s son, Hunter Biden, during the height of the laptop scandal. This revelation raises questions about the role these platforms play in spreading or withholding information, as well as the direct impact this has on democracy. ## **Meta and Censorship: Zuckerberg's Letter** In his letter, Zuckerberg admitted that Facebook was pressured by the Biden administration to suppress information about the pandemic and the Hunter Biden case, something he now claims to regret. This has sparked heated debate about how far social media should go in yielding to governmental pressure. Many see this as a threat to freedom of speech, while others argue that this censorship was necessary to control misinformation. The issue here is not just about government pressure, but the fact that Facebook, as a global platform with billions of users, holds unparalleled power to shape narratives. When a platform decides what is “acceptable” or “truthful,” it directly influences public perception and opinion formation, especially during critical moments like an election. Zuckerberg, in his letter, seems to be trying to salvage his image, but the damage has already been done. The admission that Facebook collaborated with the government to suppress certain information raises doubts about the platform’s impartiality and its commitment to free speech. ## **Elon Musk and Free Speech on X** Meanwhile, Elon Musk, now in control of Twitter, renamed X, has promised to transform the platform into a space for free expression. However, the reality seems more complex. Musk claims that X should be a place where all voices can be heard, regardless of political or ideological alignment. Yet, this promise has proven difficult to fulfill in practice. X continues to ban users and censor content, especially in countries with authoritarian governments like India and Turkey. This creates a dichotomy: on the one hand, Musk advocates for unrestricted free speech, but on the other, he complies with censorship requests from these regimes. This raises questions about Musk’s true intentions and the extent to which he is willing to uphold his principles when the platform faces international pressure. Moreover, Musk has used X as a political platform, especially in support of former President Donald Trump. The reinstatement of Trump’s account, banned during the Capitol insurrection, has raised further suspicions that Musk is turning X into a tool of political power. For many, this represents a significant risk to the neutrality of digital platforms. ## **The Cambridge Analytica Scandal and the Risk of Political Manipulation** The discussion of censorship and free speech on social media brings up a case that shocked the world a few years ago: the Cambridge Analytica scandal. In 2015, this British company was accused of using personal data from millions of Facebook users to manipulate elections, including the Brexit referendum and Donald Trump’s 2016 presidential election. Although Cambridge Analytica was dissolved after the scandal, its legacy remains. Big Tech companies still have access to vast amounts of user data, and the power this grants them is alarming. Companies like Meta and X could, in theory, directly influence election outcomes by manipulating algorithms to promote certain narratives or suppress others. This scenario raises crucial questions: to what extent can we trust these platforms to act impartially? Are they truly committed to free speech, or are they using their power to shape the political future of the world according to their own interests? ## **The Pablo Marçal Case and Manipulation in Brazil** In Brazil, a recent example that illustrates the complexity of the relationship between social media and political power is the case of coach Pablo Marçal. Marçal, who built a considerable following, became involved in controversies related to using his influence to manipulate public opinion. Recently, it was revealed that X hired the renowned law firm Pinheiro Neto to defend Marçal’s continued presence on the platform, even after controversies. This move raises concerns about the selective enforcement of social media’s own rules. Why are some influencers protected while others are summarily banned? Marçal’s influence, particularly among conservative voters in Brazil, is undeniable, and the public defense of his account on X suggests that more is at stake than just free speech. ## **The Future of Social Media and Democracy** What we are witnessing is the rise of a new era where social media plays a central role in global politics. Control over the flow of information lies in the hands of a few giant companies, and the decisions of their leaders—whether Mark Zuckerberg, Elon Musk, or others—can have a profound impact on elections, governments, and democracies. This raises legitimate concerns about the future of democracy in a world where private platforms have the power to control public discourse. Big Tech censorship, often disguised as “misinformation control,” can easily become a tool for manipulation. For citizens, this means being vigilant and critical about the information they receive on social media. Freedom of expression must be defended, but we also need to question who is behind these platforms and what their true motivations are. Trust in social media is at stake, and the future of democracy may depend on how we decide to deal with this unprecedented power. ## **Conclusion** Recent revelations about Zuckerberg’s involvement in censorship and Musk’s use of X to promote a political agenda highlight the urgent need for transparency in social media platforms. As these companies become increasingly influential in the global political arena, the public must be aware of the risks and actively engage in the debate about the future of free speech and democracy.
@ eac63075:b4988b48
2024-10-10 18:12:38Companies like Meta (formerly Facebook) and Twitter (now X) control platforms that have become the main channels of communication for millions of people worldwide. At the center of this discussion are figures like Mark Zuckerberg and Elon Musk, whose recent actions raise serious questions about freedom of speech, censorship, and political manipulation. --- <https://fountain.fm/episode/VzJItfySZ8z6417prHyD> --- Recently, a public letter written by Mark Zuckerberg revealed how the U.S. government, under Joe Biden’s administration, pressured Facebook to censor information during the COVID-19 pandemic. The controversy involves, among other topics, the censorship of content related to Biden’s son, Hunter Biden, during the height of the laptop scandal. This revelation raises questions about the role these platforms play in spreading or withholding information, as well as the direct impact this has on democracy. ## **Meta and Censorship: Zuckerberg's Letter** In his letter, Zuckerberg admitted that Facebook was pressured by the Biden administration to suppress information about the pandemic and the Hunter Biden case, something he now claims to regret. This has sparked heated debate about how far social media should go in yielding to governmental pressure. Many see this as a threat to freedom of speech, while others argue that this censorship was necessary to control misinformation. The issue here is not just about government pressure, but the fact that Facebook, as a global platform with billions of users, holds unparalleled power to shape narratives. When a platform decides what is “acceptable” or “truthful,” it directly influences public perception and opinion formation, especially during critical moments like an election. Zuckerberg, in his letter, seems to be trying to salvage his image, but the damage has already been done. The admission that Facebook collaborated with the government to suppress certain information raises doubts about the platform’s impartiality and its commitment to free speech. ## **Elon Musk and Free Speech on X** Meanwhile, Elon Musk, now in control of Twitter, renamed X, has promised to transform the platform into a space for free expression. However, the reality seems more complex. Musk claims that X should be a place where all voices can be heard, regardless of political or ideological alignment. Yet, this promise has proven difficult to fulfill in practice. X continues to ban users and censor content, especially in countries with authoritarian governments like India and Turkey. This creates a dichotomy: on the one hand, Musk advocates for unrestricted free speech, but on the other, he complies with censorship requests from these regimes. This raises questions about Musk’s true intentions and the extent to which he is willing to uphold his principles when the platform faces international pressure. Moreover, Musk has used X as a political platform, especially in support of former President Donald Trump. The reinstatement of Trump’s account, banned during the Capitol insurrection, has raised further suspicions that Musk is turning X into a tool of political power. For many, this represents a significant risk to the neutrality of digital platforms. ## **The Cambridge Analytica Scandal and the Risk of Political Manipulation** The discussion of censorship and free speech on social media brings up a case that shocked the world a few years ago: the Cambridge Analytica scandal. In 2015, this British company was accused of using personal data from millions of Facebook users to manipulate elections, including the Brexit referendum and Donald Trump’s 2016 presidential election. Although Cambridge Analytica was dissolved after the scandal, its legacy remains. Big Tech companies still have access to vast amounts of user data, and the power this grants them is alarming. Companies like Meta and X could, in theory, directly influence election outcomes by manipulating algorithms to promote certain narratives or suppress others. This scenario raises crucial questions: to what extent can we trust these platforms to act impartially? Are they truly committed to free speech, or are they using their power to shape the political future of the world according to their own interests? ## **The Pablo Marçal Case and Manipulation in Brazil** In Brazil, a recent example that illustrates the complexity of the relationship between social media and political power is the case of coach Pablo Marçal. Marçal, who built a considerable following, became involved in controversies related to using his influence to manipulate public opinion. Recently, it was revealed that X hired the renowned law firm Pinheiro Neto to defend Marçal’s continued presence on the platform, even after controversies. This move raises concerns about the selective enforcement of social media’s own rules. Why are some influencers protected while others are summarily banned? Marçal’s influence, particularly among conservative voters in Brazil, is undeniable, and the public defense of his account on X suggests that more is at stake than just free speech. ## **The Future of Social Media and Democracy** What we are witnessing is the rise of a new era where social media plays a central role in global politics. Control over the flow of information lies in the hands of a few giant companies, and the decisions of their leaders—whether Mark Zuckerberg, Elon Musk, or others—can have a profound impact on elections, governments, and democracies. This raises legitimate concerns about the future of democracy in a world where private platforms have the power to control public discourse. Big Tech censorship, often disguised as “misinformation control,” can easily become a tool for manipulation. For citizens, this means being vigilant and critical about the information they receive on social media. Freedom of expression must be defended, but we also need to question who is behind these platforms and what their true motivations are. Trust in social media is at stake, and the future of democracy may depend on how we decide to deal with this unprecedented power. ## **Conclusion** Recent revelations about Zuckerberg’s involvement in censorship and Musk’s use of X to promote a political agenda highlight the urgent need for transparency in social media platforms. As these companies become increasingly influential in the global political arena, the public must be aware of the risks and actively engage in the debate about the future of free speech and democracy. @ c69b71dc:426ba763
2024-10-10 09:05:29## Chef's notes This cashew blue cheese is a true plant-based delight, delivering the rich, tangy flavours you’d expect from traditional blue cheeses like Roquefort or Gorgonzola. The fermentation process, with the help of «Penicillium Roqueforti», creates a beautifully marbled, creamy cheese that’s both bold and complex. It’s a labor of love that rewards your patience with an unforgettable vegan cheese experience! Whether enjoyed on crackers, in salads, or simply on its own, this cheese will elevate any dish with its unique flavour profile. Note 1: For this recipe you need parchment paper, a potent blender, glass jars with lid and two cheesecloths. Note 2: Always use very clean tools, and avoid touching with your fingers or tasting with them while working on the cheese! ## Details - ⏲️ Prep time: 4-5 weeks - 🍳 Cook time: 0 - 🍽️ Servings: Two small cheese loaves (2x 10-12 cm diameter) ## Ingredients - 300g raw cashews - 3 tbsp water - 3 tbsp kefir, kombucha or rejuvelac - 2 tbsp coconut oil (raw, unrefined) - 1-4 capsules vegan probiotics - 1/2 tsp Himalayan salt (iodine-free, no additives) - 1/16 tsp «Penicillium Roqueforti» (blue cheese mold culture) ## Directions 1. Day 1: Soak 300g of cashews overnight in water. 2. Day 2: Rinse the soaked cashews thoroughly and let them drain well. 3. In a high-speed blender, combine the cashews, 3 tbsp of water, 3 tbsp kefir or rejuvelac, and 2 tbsp coconut oil. Blend until the mixture is smooth and creamy. 4. Add 1-4 capsules of vegan probiotics, 1/2 tsp Himalayan salt (free of iodine and additives), and blend again briefly. 5. Add a pinch (about 1/16 tsp) of «Penicillium Roqueforti» powder (blue cheese culture) and give it another quick mix. 6. Transfer the cashew mixture to a glass container, leaving the lid lightly on top (do not seal it completely) and store in a warm place, ideally in your kitchen, for 24 hours to ferment. 7. Day 3: Divide the fermented cashew mixture into two smaller glass containers lined with cheesecloth. Press the mixture down firmly to eliminate air pockets. 8. Store in a cool place (12-14°C / 53-57°F), ideally in a wine fridge. 9. Day 4: Remove the cheese from the containers, take off the cheesecloth, and turn the cheese onto parchment paper. 10. Sprinkle salt all over the cheese, ensuring it is evenly coated. 11. Cover the cheese with larger glass bowls, ensuring that air can flow from underneath, and return to the wine fridge or the cool storage area. 12. Days 4-7: Turn the cheese daily onto fresh parchment paper to maintain its texture. 13. Day 7 or 8: Pierce the cheese with a thicker wooden skewer to create holes, allowing oxygen to reach the center, encouraging the blue mold to grow throughout the cheese, not just on the surface. 14. Alternatively, crumble the cheese completely and then press it back into shape to ensure oxygen distribution. 15. Days 8 toaround 12 or 15: Once the blue mold has fully developed around and inside the cheese, wrap the cheese in parchment paper, place it in a wooden cheese box, and then wrap it in a cloth bag. 16. Transfer to a regular fridge to age for another 2-3 weeks or even several months, depending on your desired strength of flavour.
@ c69b71dc:426ba763
2024-10-10 09:05:29## Chef's notes This cashew blue cheese is a true plant-based delight, delivering the rich, tangy flavours you’d expect from traditional blue cheeses like Roquefort or Gorgonzola. The fermentation process, with the help of «Penicillium Roqueforti», creates a beautifully marbled, creamy cheese that’s both bold and complex. It’s a labor of love that rewards your patience with an unforgettable vegan cheese experience! Whether enjoyed on crackers, in salads, or simply on its own, this cheese will elevate any dish with its unique flavour profile. Note 1: For this recipe you need parchment paper, a potent blender, glass jars with lid and two cheesecloths. Note 2: Always use very clean tools, and avoid touching with your fingers or tasting with them while working on the cheese! ## Details - ⏲️ Prep time: 4-5 weeks - 🍳 Cook time: 0 - 🍽️ Servings: Two small cheese loaves (2x 10-12 cm diameter) ## Ingredients - 300g raw cashews - 3 tbsp water - 3 tbsp kefir, kombucha or rejuvelac - 2 tbsp coconut oil (raw, unrefined) - 1-4 capsules vegan probiotics - 1/2 tsp Himalayan salt (iodine-free, no additives) - 1/16 tsp «Penicillium Roqueforti» (blue cheese mold culture) ## Directions 1. Day 1: Soak 300g of cashews overnight in water. 2. Day 2: Rinse the soaked cashews thoroughly and let them drain well. 3. In a high-speed blender, combine the cashews, 3 tbsp of water, 3 tbsp kefir or rejuvelac, and 2 tbsp coconut oil. Blend until the mixture is smooth and creamy. 4. Add 1-4 capsules of vegan probiotics, 1/2 tsp Himalayan salt (free of iodine and additives), and blend again briefly. 5. Add a pinch (about 1/16 tsp) of «Penicillium Roqueforti» powder (blue cheese culture) and give it another quick mix. 6. Transfer the cashew mixture to a glass container, leaving the lid lightly on top (do not seal it completely) and store in a warm place, ideally in your kitchen, for 24 hours to ferment. 7. Day 3: Divide the fermented cashew mixture into two smaller glass containers lined with cheesecloth. Press the mixture down firmly to eliminate air pockets. 8. Store in a cool place (12-14°C / 53-57°F), ideally in a wine fridge. 9. Day 4: Remove the cheese from the containers, take off the cheesecloth, and turn the cheese onto parchment paper. 10. Sprinkle salt all over the cheese, ensuring it is evenly coated. 11. Cover the cheese with larger glass bowls, ensuring that air can flow from underneath, and return to the wine fridge or the cool storage area. 12. Days 4-7: Turn the cheese daily onto fresh parchment paper to maintain its texture. 13. Day 7 or 8: Pierce the cheese with a thicker wooden skewer to create holes, allowing oxygen to reach the center, encouraging the blue mold to grow throughout the cheese, not just on the surface. 14. Alternatively, crumble the cheese completely and then press it back into shape to ensure oxygen distribution. 15. Days 8 toaround 12 or 15: Once the blue mold has fully developed around and inside the cheese, wrap the cheese in parchment paper, place it in a wooden cheese box, and then wrap it in a cloth bag. 16. Transfer to a regular fridge to age for another 2-3 weeks or even several months, depending on your desired strength of flavour. @ aa8de34f:a6ffe696
2024-10-09 21:56:39\`\`\` Technion - Israel Institute of Technology\ Foundations of Quantum Mechanics\ Date: 2024-08-25 Submitted by: Max Peter \`\`\` \# Quantum Mechanics and Consciousness: Strange Bedfellows *"Does consciousness play a special role in quantum mechanics?"* ## Abstract Could there be a connection between quantum mechanics and consciousness? This Question has fascinated scholars for years. Some believe that consciousness plays a role in how we interpret quantum theory. This essay explores whether consciousness is a fundamental component of quantum mechanics, addressing both the "hard problem" of consciousness and the various interpretations of quantum theory. By critically analyzing arguments from prominent figures like David Chalmers and Barry Loewer, the essay argues that while consciousness presents a significant challenge in understanding reality, current quantum theories may not provide the final answers. Instead, the *"hard problem"* of consciousness could be the unresolved issue that quantum mechanics needs to address, making it the *"elephant in the room"* that scientists often avoid. ## 1. Introduction The relationship between quantum mechanics and consciousness is one of the most intriguing and contentious debates in modern science and philosophy. Quantum mechanics, the physics of the very small, has upended our classical understanding of the universe, introducing phenomena such as superposition, entanglement, and wavefunction collapse that defy intuition. Simultaneously, consciousness - the subjective experience of being aware - remains one of the most profound mysteries in science, famously described by David Chalmers (1995) as the "hard problem." The intersection of these two enigmatic fields has led to the proposal that consciousness may play a special role in quantum mechanics, particularly in the process of wavefunction collapse, where observation seems to determine physical reality. This essay explores the question: Does consciousness play a special role in quantum mechanics? Advocates of this idea, such as Wigner and Stapp, have argued that consciousness is not merely an observer in quantum mechanics but an active participant that influences quantum events. However, this view is not without its critics. Many physicists and philosophers, including Barry Loewer, argue that connecting consciousness to quantum mechanics is speculative and unsupported by empirical evidence. Despite these criticisms, the possibility that consciousness could be the "elephant in the room" that quantum mechanics needs to address remains an open question. This essay will explore the various interpretations of quantum mechanics that engage with or avoid the issue of consciousness and will argue that the hard problem of consciousness is maybe a vital, yet often ignored, aspect of a better understanding of quantum physics. ## 2. The Basics of Quantum Mechanics Quantum mechanics is the branch of physics that deals with the behavior of particles at the smallest scale - atoms and subatomic particles. It is governed by principles that are vastly different from the deterministic laws of classical physics. One of the foundational concepts of quantum mechanics is the wavefunction, a mathematical function that describes the probabilities of a particle's properties, such as position and momentum. Unlike in classical mechanics, where a particle has a definite position and momentum, in quantum mechanics, these properties are described by a probability distribution. One of the most famous principles of quantum mechanics is superposition, which states that a particle can exist in multiple states simultaneously until it is observed. This is famously illustrated by Schrödinger's cat thought experiment, where a cat in a box is simultaneously alive and dead until the box is opened, and an observation is made. Another critical concept is entanglement, where particles become linked, so the state of one particle instantaneously affects the state of another, regardless of the distance between them. The wavefunction collapse is perhaps the most perplexing aspect of quantum mechanics. When a quantum system is observed, the wavefunction collapses, and the system settles into a definite state. This raises the question: What causes the wavefunction to collapse? Is it the act of measurement itself, or does consciousness play a role in this process? The measurement problem in quantum mechanics has led some to propose that consciousness is necessary for wavefunction collapse, thus connecting the two fields in a profound way. ## 3. The Hard Problem of Consciousness David Chalmers (1995) famously distinguished between the "easy" and "hard" problems of consciousness. The easy problems involve explaining the cognitive functions and processes that underlie perception, memory, and behavior. These problems, while challenging, are considered solvable through the standard methods of cognitive science and neuroscience. The hard problem, on the other hand, is the problem of subjective experience - why and how physical processes in the brain give rise to the rich inner life of sensation, emotion, and awareness. This subjective aspect of consciousness, also known as qualia (Latin “of what sort”), remains resistant to reductive explanation. Chalmers (1995) argues that the hard problem of consciousness cannot be solved by merely explaining the functions of the brain. There is a gap between physical processes and the experience of those processes - a gap that traditional science struggles to bridge. This has led some theorists to propose that consciousness might be fundamental to the universe, rather than a byproduct of physical processes. This idea has significant implications for quantum mechanics, particularly in the context of the measurement problem. If consciousness is indeed fundamental, it may play a direct role in the collapse of the wavefunction, linking the hard problem of consciousness with the mysteries of quantum mechanics. ## 4. Consciousness and Quantum Mechanics The idea that consciousness plays a special role in quantum mechanics is most closely associated with the Consciousness Collapse Proposal (CCP). This theory suggests that the act of observation by a conscious being is what causes the wavefunction to collapse into a definite state. This view was championed by physicists like Eugene Wigner and Henry Stapp, who argued that consciousness must be integrated into our understanding of quantum mechanics. According to Wigner, consciousness is the ultimate cause of the wavefunction collapse, implying that the physical world does not exist in a definite state until it is observed by a conscious mind (Wigner, 1967). However, the CCP is not without its critics. Barry Loewer (2003) argues that the connection between consciousness and quantum mechanics is speculative and lacks empirical support. He contends that while quantum mechanics may involve strange and counterintuitive phenomena, there is no evidence that consciousness plays a direct role in these processes. Loewer suggests that alternative interpretations of quantum mechanics, such as the Ghirardi-Rimini-Weber (GRW) theory and Bohmian mechanics, offer explanations for wavefunction collapse that do not require the involvement of consciousness (Loewer, 2003). Despite these criticisms, the idea that consciousness could be fundamental to quantum mechanics remains a compelling possibility. The CCP aligns with the notion that consciousness is not just an epiphenomenon of brain activity but a fundamental aspect of reality. This perspective challenges the materialist view that physical processes alone are sufficient to explain all phenomena, including consciousness. Instead, it suggests that consciousness might be the key to resolving the mysteries of quantum mechanics. ## 5. The Elephant in the Room: The Hard Problem of Consciousness in Quantum Mechanics The central thesis of this section is that the hard problem of consciousness, as articulated by David Chalmers (1995), represents an unresolved issue in the interpretation of quantum mechanics, and may be the "elephant in the room" that most scientific theories attempt to avoid. While many physicists adopt materialist interpretations of quantum mechanics that sidestep the issue of consciousness, it is increasingly difficult to ignore the possibility that consciousness might play a fundamental role in the behaviour of quantum systems. This section will argue that the hard problem of consciousness is not just a philosophical curiosity but a crucial component in understanding the true nature of quantum mechanics. ### Consciousness as a Fundamental Aspect of Reality The hard problem of consciousness refers to the challenge of explaining how and why physical processes in the brain give rise to subjective experience—what it feels like to perceive, think, and be aware. Chalmers (1995) argues that the hard problem is distinct from the "easy" problems of explaining cognitive functions and behaviours because it involves the subjective nature of experience, which cannot be fully captured by a purely physical explanation. This problem is central to the question of whether consciousness plays a role in quantum mechanics because it challenges the materialist assumption that everything can be explained in terms of physical processes. One argument in favour of consciousness playing a fundamental role in quantum mechanics is that it may help solve the measurement problem—the question of why and how the wavefunction collapses when a measurement is made. According to the Consciousness Collapse Proposal (CCP), the collapse of the wavefunction occurs when a conscious observer interacts with the system, suggesting that consciousness is a necessary component of reality. This idea challenges the traditional view of quantum mechanics as a purely objective, observer-independent theory and implies that consciousness is more than just a byproduct of physical processes (Stapp, 1993). In this view, consciousness is not simply an epiphenomenon of the brain but a fundamental aspect of reality that interacts with the physical world in a way that science has yet to fully understand. This perspective aligns with certain interpretations of quantum mechanics, such as the von Neumann-Wigner interpretation, which posits that consciousness plays an active role in the collapse of the wavefunction. While this interpretation remains controversial, it highlights the possibility that consciousness could be integral to the functioning of the universe at a fundamental level. ### Avoidance of the Hard Problem in Mainstream Science Despite the compelling nature of the hard problem, mainstream scientific interpretations of quantum mechanics often avoid addressing consciousness directly. For example, the Many Worlds Interpretation (MWI) of quantum mechanics sidesteps the issue of wavefunction collapse altogether by proposing that all possible outcomes of a quantum measurement exist simultaneously in parallel worlds. In this framework, there is no need to invoke consciousness as a factor in determining the outcome of a quantum event, as every possible outcome is realized in some branch of the multiverse (Everett, 1957). While MWI elegantly avoids the problem of collapse, it does so at the cost of ignoring the role of consciousness, which remains unexplained. Similarly, the Ghirardi-Rimini-Weber (GRW) theory offers an objective collapse model that introduces spontaneous collapses of the wavefunction, independent of observation or consciousness. This theory attempts to solve the measurement problem without invoking consciousness by suggesting that wavefunctions collapse randomly after a certain threshold is reached (Ghirardi, Rimini, & Weber, 1986). Although GRW provides a mathematically consistent solution to the measurement problem, it does not address the hard problem of consciousness, leaving the nature of subjective experience untouched. These interpretations reflect a broader tendency in science to focus on solving the technical aspects of quantum mechanics while avoiding the deeper philosophical questions about consciousness. This approach is understandable, given that the hard problem of consciousness is notoriously difficult to address within the framework of materialist science. However, by sidestepping the issue, these interpretations may be missing a crucial piece of the puzzle. If consciousness is indeed fundamental to the collapse of the wavefunction, as proponents of the CCP suggest, then any interpretation that ignores consciousness is inherently incomplete. ### The Case for Addressing Consciousness in Quantum Mechanics Given the limitations of current interpretations of quantum mechanics, there is a strong case to be made for addressing the hard problem of consciousness directly. One of the key challenges in integrating consciousness into quantum mechanics is the lack of empirical evidence linking consciousness to wavefunction collapse. Critics like Barry Loewer (2003) argue that the CCP is speculative and lacks the rigorous experimental support needed to be taken seriously as a scientific theory. This criticism is valid, as science requires empirical validation to support theoretical claims. However, the absence of empirical evidence does not necessarily invalidate the idea that consciousness could play a role in quantum mechanics. The lack of direct evidence may simply reflect the limitations of current experimental methods, which are not yet sophisticated enough to test the relationship between consciousness and quantum phenomena. Furthermore, the hard problem of consciousness remains unresolved by conventional science, suggesting that new approaches may be needed to explore the connection between consciousness and the physical world. In response to critics, proponents of the CCP could argue that quantum mechanics itself has a long history of challenging conventional notions of reality. The very existence of phenomena like entanglement and superposition defies classical logic and suggests that our understanding of the universe is incomplete. If consciousness is indeed fundamental to the fabric of reality, then it is possible that it plays a role in these quantum phenomena in ways that we do not yet fully understand. Rather than dismissing the CCP as speculative, it may be more productive to consider it as a potential avenue for further research, one that could ultimately lead to a deeper understanding of both consciousness and quantum mechanics. ## 6. Personal Viewpoint: Consciousness as a Vital Component in Quantum Mechanics In my view, the hard problem of consciousness is not just an interesting philosophical challenge but a vital issue that must be addressed if we are to fully understand quantum mechanics. The reluctance of many scientists to engage with the hard problem is understandable, given the difficulty of the question and the lack of empirical evidence. However, this avoidance may be preventing us from making significant progress in understanding the true nature of reality. I believe that the hard problem of consciousness represents a fundamental gap in our understanding of the universe - one that cannot be ignored if we are to develop a complete theory of quantum mechanics. While alternative interpretations like the GRW theory and the Many Worlds Interpretation offer solutions to the technical problems of quantum mechanics, they do so by avoiding the deeper question of consciousness. This approach, while pragmatic, may ultimately prove to be a dead end if consciousness is indeed integral to the behaviour of quantum systems. Addressing the hard problem of consciousness in the context of quantum mechanics requires a willingness to think beyond the current boundaries of science and to explore new theoretical frameworks that integrate consciousness into our understanding of the physical world. This may involve revisiting ideas like the Consciousness Collapse Proposal or developing entirely new theories that link consciousness with quantum phenomena in ways that we have not yet imagined. At the same time, it is important to approach this question with a critical and balanced perspective. While the idea that consciousness plays a role in quantum mechanics is intriguing, it is essential to remain open to alternative explanations and to demand rigorous empirical evidence to support any claims. The history of science is filled with theories that seemed promising but ultimately proved to be incorrect, and we must be careful not to fall into the trap of speculation without evidence. ## Conclusion In Summary, I believe that the hard problem of consciousness is the *"elephant in the room"* that quantum mechanics needs to address. While traditional interpretations of quantum theory have tried to solve the measurement problem without involving consciousness it might be ignoring a part of reality. By blending the matter of consciousness into quantum mechanics we could potentially gain a comprehensive view of the universe - one that appreciates both the enigmatic nature of subjective experiences and the elegant mathematics of some quantum mechanics theories. Even though this viewpoint is speculative and needs investigation it presents a glimpse into a future where consciousness and quantum mechanics are seen as interconnected elements of existence. ### References \- CHALMERS, D. J. (1995). FACING UP TO THE PROBLEM OF CONSCIOUSNESS. JOURNAL OF CONSCIOUSNESS STUDIES, 2(3), 200-219. \- EVERETT, H. (1957). “RELATIVE STATE” FORMULATION OF QUANTUM MECHANICS. REVIEWS OF MODERN PHYSICS, 29(3), 454-462. \- GHIRARDI, G. C., RIMINI, A., & WEBER, T. (1986). UNIFIED DYNAMICS FOR MICROSCOPIC AND MACROSCOPIC SYSTEMS. PHYSICAL REVIEW D, 34(2), 470-491. \- LOEWER, B. (2003). CONSCIOUSNESS AND QUANTUM THEORY: STRANGE BEDFELLOWS. \- STAPP, H. P. (1993). MIND, MATTER, AND QUANTUM MECHANICS. SPRINGER.
@ aa8de34f:a6ffe696
2024-10-09 21:56:39\`\`\` Technion - Israel Institute of Technology\ Foundations of Quantum Mechanics\ Date: 2024-08-25 Submitted by: Max Peter \`\`\` \# Quantum Mechanics and Consciousness: Strange Bedfellows *"Does consciousness play a special role in quantum mechanics?"* ## Abstract Could there be a connection between quantum mechanics and consciousness? This Question has fascinated scholars for years. Some believe that consciousness plays a role in how we interpret quantum theory. This essay explores whether consciousness is a fundamental component of quantum mechanics, addressing both the "hard problem" of consciousness and the various interpretations of quantum theory. By critically analyzing arguments from prominent figures like David Chalmers and Barry Loewer, the essay argues that while consciousness presents a significant challenge in understanding reality, current quantum theories may not provide the final answers. Instead, the *"hard problem"* of consciousness could be the unresolved issue that quantum mechanics needs to address, making it the *"elephant in the room"* that scientists often avoid. ## 1. Introduction The relationship between quantum mechanics and consciousness is one of the most intriguing and contentious debates in modern science and philosophy. Quantum mechanics, the physics of the very small, has upended our classical understanding of the universe, introducing phenomena such as superposition, entanglement, and wavefunction collapse that defy intuition. Simultaneously, consciousness - the subjective experience of being aware - remains one of the most profound mysteries in science, famously described by David Chalmers (1995) as the "hard problem." The intersection of these two enigmatic fields has led to the proposal that consciousness may play a special role in quantum mechanics, particularly in the process of wavefunction collapse, where observation seems to determine physical reality. This essay explores the question: Does consciousness play a special role in quantum mechanics? Advocates of this idea, such as Wigner and Stapp, have argued that consciousness is not merely an observer in quantum mechanics but an active participant that influences quantum events. However, this view is not without its critics. Many physicists and philosophers, including Barry Loewer, argue that connecting consciousness to quantum mechanics is speculative and unsupported by empirical evidence. Despite these criticisms, the possibility that consciousness could be the "elephant in the room" that quantum mechanics needs to address remains an open question. This essay will explore the various interpretations of quantum mechanics that engage with or avoid the issue of consciousness and will argue that the hard problem of consciousness is maybe a vital, yet often ignored, aspect of a better understanding of quantum physics. ## 2. The Basics of Quantum Mechanics Quantum mechanics is the branch of physics that deals with the behavior of particles at the smallest scale - atoms and subatomic particles. It is governed by principles that are vastly different from the deterministic laws of classical physics. One of the foundational concepts of quantum mechanics is the wavefunction, a mathematical function that describes the probabilities of a particle's properties, such as position and momentum. Unlike in classical mechanics, where a particle has a definite position and momentum, in quantum mechanics, these properties are described by a probability distribution. One of the most famous principles of quantum mechanics is superposition, which states that a particle can exist in multiple states simultaneously until it is observed. This is famously illustrated by Schrödinger's cat thought experiment, where a cat in a box is simultaneously alive and dead until the box is opened, and an observation is made. Another critical concept is entanglement, where particles become linked, so the state of one particle instantaneously affects the state of another, regardless of the distance between them. The wavefunction collapse is perhaps the most perplexing aspect of quantum mechanics. When a quantum system is observed, the wavefunction collapses, and the system settles into a definite state. This raises the question: What causes the wavefunction to collapse? Is it the act of measurement itself, or does consciousness play a role in this process? The measurement problem in quantum mechanics has led some to propose that consciousness is necessary for wavefunction collapse, thus connecting the two fields in a profound way. ## 3. The Hard Problem of Consciousness David Chalmers (1995) famously distinguished between the "easy" and "hard" problems of consciousness. The easy problems involve explaining the cognitive functions and processes that underlie perception, memory, and behavior. These problems, while challenging, are considered solvable through the standard methods of cognitive science and neuroscience. The hard problem, on the other hand, is the problem of subjective experience - why and how physical processes in the brain give rise to the rich inner life of sensation, emotion, and awareness. This subjective aspect of consciousness, also known as qualia (Latin “of what sort”), remains resistant to reductive explanation. Chalmers (1995) argues that the hard problem of consciousness cannot be solved by merely explaining the functions of the brain. There is a gap between physical processes and the experience of those processes - a gap that traditional science struggles to bridge. This has led some theorists to propose that consciousness might be fundamental to the universe, rather than a byproduct of physical processes. This idea has significant implications for quantum mechanics, particularly in the context of the measurement problem. If consciousness is indeed fundamental, it may play a direct role in the collapse of the wavefunction, linking the hard problem of consciousness with the mysteries of quantum mechanics. ## 4. Consciousness and Quantum Mechanics The idea that consciousness plays a special role in quantum mechanics is most closely associated with the Consciousness Collapse Proposal (CCP). This theory suggests that the act of observation by a conscious being is what causes the wavefunction to collapse into a definite state. This view was championed by physicists like Eugene Wigner and Henry Stapp, who argued that consciousness must be integrated into our understanding of quantum mechanics. According to Wigner, consciousness is the ultimate cause of the wavefunction collapse, implying that the physical world does not exist in a definite state until it is observed by a conscious mind (Wigner, 1967). However, the CCP is not without its critics. Barry Loewer (2003) argues that the connection between consciousness and quantum mechanics is speculative and lacks empirical support. He contends that while quantum mechanics may involve strange and counterintuitive phenomena, there is no evidence that consciousness plays a direct role in these processes. Loewer suggests that alternative interpretations of quantum mechanics, such as the Ghirardi-Rimini-Weber (GRW) theory and Bohmian mechanics, offer explanations for wavefunction collapse that do not require the involvement of consciousness (Loewer, 2003). Despite these criticisms, the idea that consciousness could be fundamental to quantum mechanics remains a compelling possibility. The CCP aligns with the notion that consciousness is not just an epiphenomenon of brain activity but a fundamental aspect of reality. This perspective challenges the materialist view that physical processes alone are sufficient to explain all phenomena, including consciousness. Instead, it suggests that consciousness might be the key to resolving the mysteries of quantum mechanics. ## 5. The Elephant in the Room: The Hard Problem of Consciousness in Quantum Mechanics The central thesis of this section is that the hard problem of consciousness, as articulated by David Chalmers (1995), represents an unresolved issue in the interpretation of quantum mechanics, and may be the "elephant in the room" that most scientific theories attempt to avoid. While many physicists adopt materialist interpretations of quantum mechanics that sidestep the issue of consciousness, it is increasingly difficult to ignore the possibility that consciousness might play a fundamental role in the behaviour of quantum systems. This section will argue that the hard problem of consciousness is not just a philosophical curiosity but a crucial component in understanding the true nature of quantum mechanics. ### Consciousness as a Fundamental Aspect of Reality The hard problem of consciousness refers to the challenge of explaining how and why physical processes in the brain give rise to subjective experience—what it feels like to perceive, think, and be aware. Chalmers (1995) argues that the hard problem is distinct from the "easy" problems of explaining cognitive functions and behaviours because it involves the subjective nature of experience, which cannot be fully captured by a purely physical explanation. This problem is central to the question of whether consciousness plays a role in quantum mechanics because it challenges the materialist assumption that everything can be explained in terms of physical processes. One argument in favour of consciousness playing a fundamental role in quantum mechanics is that it may help solve the measurement problem—the question of why and how the wavefunction collapses when a measurement is made. According to the Consciousness Collapse Proposal (CCP), the collapse of the wavefunction occurs when a conscious observer interacts with the system, suggesting that consciousness is a necessary component of reality. This idea challenges the traditional view of quantum mechanics as a purely objective, observer-independent theory and implies that consciousness is more than just a byproduct of physical processes (Stapp, 1993). In this view, consciousness is not simply an epiphenomenon of the brain but a fundamental aspect of reality that interacts with the physical world in a way that science has yet to fully understand. This perspective aligns with certain interpretations of quantum mechanics, such as the von Neumann-Wigner interpretation, which posits that consciousness plays an active role in the collapse of the wavefunction. While this interpretation remains controversial, it highlights the possibility that consciousness could be integral to the functioning of the universe at a fundamental level. ### Avoidance of the Hard Problem in Mainstream Science Despite the compelling nature of the hard problem, mainstream scientific interpretations of quantum mechanics often avoid addressing consciousness directly. For example, the Many Worlds Interpretation (MWI) of quantum mechanics sidesteps the issue of wavefunction collapse altogether by proposing that all possible outcomes of a quantum measurement exist simultaneously in parallel worlds. In this framework, there is no need to invoke consciousness as a factor in determining the outcome of a quantum event, as every possible outcome is realized in some branch of the multiverse (Everett, 1957). While MWI elegantly avoids the problem of collapse, it does so at the cost of ignoring the role of consciousness, which remains unexplained. Similarly, the Ghirardi-Rimini-Weber (GRW) theory offers an objective collapse model that introduces spontaneous collapses of the wavefunction, independent of observation or consciousness. This theory attempts to solve the measurement problem without invoking consciousness by suggesting that wavefunctions collapse randomly after a certain threshold is reached (Ghirardi, Rimini, & Weber, 1986). Although GRW provides a mathematically consistent solution to the measurement problem, it does not address the hard problem of consciousness, leaving the nature of subjective experience untouched. These interpretations reflect a broader tendency in science to focus on solving the technical aspects of quantum mechanics while avoiding the deeper philosophical questions about consciousness. This approach is understandable, given that the hard problem of consciousness is notoriously difficult to address within the framework of materialist science. However, by sidestepping the issue, these interpretations may be missing a crucial piece of the puzzle. If consciousness is indeed fundamental to the collapse of the wavefunction, as proponents of the CCP suggest, then any interpretation that ignores consciousness is inherently incomplete. ### The Case for Addressing Consciousness in Quantum Mechanics Given the limitations of current interpretations of quantum mechanics, there is a strong case to be made for addressing the hard problem of consciousness directly. One of the key challenges in integrating consciousness into quantum mechanics is the lack of empirical evidence linking consciousness to wavefunction collapse. Critics like Barry Loewer (2003) argue that the CCP is speculative and lacks the rigorous experimental support needed to be taken seriously as a scientific theory. This criticism is valid, as science requires empirical validation to support theoretical claims. However, the absence of empirical evidence does not necessarily invalidate the idea that consciousness could play a role in quantum mechanics. The lack of direct evidence may simply reflect the limitations of current experimental methods, which are not yet sophisticated enough to test the relationship between consciousness and quantum phenomena. Furthermore, the hard problem of consciousness remains unresolved by conventional science, suggesting that new approaches may be needed to explore the connection between consciousness and the physical world. In response to critics, proponents of the CCP could argue that quantum mechanics itself has a long history of challenging conventional notions of reality. The very existence of phenomena like entanglement and superposition defies classical logic and suggests that our understanding of the universe is incomplete. If consciousness is indeed fundamental to the fabric of reality, then it is possible that it plays a role in these quantum phenomena in ways that we do not yet fully understand. Rather than dismissing the CCP as speculative, it may be more productive to consider it as a potential avenue for further research, one that could ultimately lead to a deeper understanding of both consciousness and quantum mechanics. ## 6. Personal Viewpoint: Consciousness as a Vital Component in Quantum Mechanics In my view, the hard problem of consciousness is not just an interesting philosophical challenge but a vital issue that must be addressed if we are to fully understand quantum mechanics. The reluctance of many scientists to engage with the hard problem is understandable, given the difficulty of the question and the lack of empirical evidence. However, this avoidance may be preventing us from making significant progress in understanding the true nature of reality. I believe that the hard problem of consciousness represents a fundamental gap in our understanding of the universe - one that cannot be ignored if we are to develop a complete theory of quantum mechanics. While alternative interpretations like the GRW theory and the Many Worlds Interpretation offer solutions to the technical problems of quantum mechanics, they do so by avoiding the deeper question of consciousness. This approach, while pragmatic, may ultimately prove to be a dead end if consciousness is indeed integral to the behaviour of quantum systems. Addressing the hard problem of consciousness in the context of quantum mechanics requires a willingness to think beyond the current boundaries of science and to explore new theoretical frameworks that integrate consciousness into our understanding of the physical world. This may involve revisiting ideas like the Consciousness Collapse Proposal or developing entirely new theories that link consciousness with quantum phenomena in ways that we have not yet imagined. At the same time, it is important to approach this question with a critical and balanced perspective. While the idea that consciousness plays a role in quantum mechanics is intriguing, it is essential to remain open to alternative explanations and to demand rigorous empirical evidence to support any claims. The history of science is filled with theories that seemed promising but ultimately proved to be incorrect, and we must be careful not to fall into the trap of speculation without evidence. ## Conclusion In Summary, I believe that the hard problem of consciousness is the *"elephant in the room"* that quantum mechanics needs to address. While traditional interpretations of quantum theory have tried to solve the measurement problem without involving consciousness it might be ignoring a part of reality. By blending the matter of consciousness into quantum mechanics we could potentially gain a comprehensive view of the universe - one that appreciates both the enigmatic nature of subjective experiences and the elegant mathematics of some quantum mechanics theories. Even though this viewpoint is speculative and needs investigation it presents a glimpse into a future where consciousness and quantum mechanics are seen as interconnected elements of existence. ### References \- CHALMERS, D. J. (1995). FACING UP TO THE PROBLEM OF CONSCIOUSNESS. JOURNAL OF CONSCIOUSNESS STUDIES, 2(3), 200-219. \- EVERETT, H. (1957). “RELATIVE STATE” FORMULATION OF QUANTUM MECHANICS. REVIEWS OF MODERN PHYSICS, 29(3), 454-462. \- GHIRARDI, G. C., RIMINI, A., & WEBER, T. (1986). UNIFIED DYNAMICS FOR MICROSCOPIC AND MACROSCOPIC SYSTEMS. PHYSICAL REVIEW D, 34(2), 470-491. \- LOEWER, B. (2003). CONSCIOUSNESS AND QUANTUM THEORY: STRANGE BEDFELLOWS. \- STAPP, H. P. (1993). MIND, MATTER, AND QUANTUM MECHANICS. SPRINGER. @ 4ba8e86d:89d32de4
2024-10-08 23:16:53Governos do mundo industrial, seus gigantes cansados de carne e aço, venho do ciberespaço, a nova casa da mente. Em nome do futuro, peço que no passado nos deixe em paz. Você não é bem vindo entre nós. Nem você exerce qualquer soberania sobre o lugar onde nos encontramos. Não elegemos nenhum governo, nem pretendemos tê-lo, por isso dirijo-me a vocês sem outra autoridade senão aquela com que sempre fala a liberdade. Declaro que o espaço social global que estamos construindo é independente por natureza das tiranias que você procura impor a nós. Você não tem o direito moral de nos governar, nem possui métodos para fazer cumprir sua lei que devemos realmente temer. Os governos obtêm seus justos poderes do consentimento daqueles que são governados. Você não pediu nem recebeu o nosso. Nós também não convidamos você. Você não nos conhece, nem conhece o nosso mundo. O ciberespaço não está dentro de suas fronteiras. Não pense que você pode construí-lo, como se fosse um projeto de construção pública. Você não pode. É um ato natural que cresce a partir de nossas ações coletivas. Você não participou de nossa grande conversa coletiva, nem criou a riqueza de nossos mercados. Você não conhece nossa cultura, nossa ética ou os códigos não escritos que já fornecem à nossa sociedade mais ordem do que o que poderia ser obtido por qualquer uma de suas imposições. Você proclama que há problemas entre nós que precisa resolver. Você usa isso como uma desculpa para invadir nossos limites. Muitos desses problemas não existem. Onde houver conflitos reais, erros, nós os identificaremos e resolveremos por nossos próprios meios. Estamos criando nosso próprio contrato social. Essa autoridade será criada de acordo com as condições do nosso mundo, não a sua. Nosso mundo é diferente. O ciberespaço é composto de transações, relacionamentos e pensamento em si, que se espalham como uma onda silenciosa na web de nossas comunicações. Nosso mundo está ao mesmo tempo em todo lugar e lugar nenhum, mas não é onde os corpos vivem. Estamos criando um mundo no qual todos possam entrar, sem privilégios ou preconceitos devido à raça, poder econômico, força militar ou local de nascimento. Estamos criando um mundo em que qualquer pessoa, em qualquer lugar, possa expressar suas crenças, não importa quão únicas sejam, sem medo de ser coagida ao silêncio ou à conformidade. Seus conceitos legais de propriedade, expressão, identidade, movimento e contexto não se aplicam a nós. Eles são baseados na matéria. Não há problema aqui. Nossas identidades não têm corpo; portanto, diferentemente de você, não podemos obter ordem por coerção física. Acreditamos que nossa autoridade emanará da moralidade, do interesse próprio progressivo e do bem comum. Nossas identidades podem ser distribuídas por várias jurisdições. A única lei que todas as nossas culturas reconheceriam é a Regra de Ouro. Esperamos ansiosamente desenvolver nossas soluções específicas sobre essa base. Mas não podemos aceitar as soluções que você está tentando impor. Hoje, na América, você criou uma lei, a Lei de Reforma das Telecomunicações, que repudia sua própria Constituição e insulta os sonhos de Jefferson, Washington, Mill, Madison, DeToqueville e Brandeis. Esses sonhos devem renascer em nós agora. Você tem medo de seus próprios filhos, pois eles são nativos em um mundo onde você sempre será imigrante. Ao recear, confia à sua burocracia responsabilidades parentais que não pode ser covarde. Em nosso mundo, todos os sentimentos e expressões da humanidade, do mais vil ao mais angélico, fazem parte de um único todo, a conversa global de bits. Não podemos separar o ar que sufoca daquele em que as asas batem. Na China, Alemanha, França, Rússia, Cingapura, Itália e Estados Unidos, você está tentando evitar o vírus da liberdade, estabelecendo postos de guarda nas fronteiras do ciberespaço. Eles podem impedir o contágio por um curto período de tempo, mas não funcionarão em um mundo que em breve será coberto pela mídia transmitida por bits. Suas indústrias de informação cada vez mais obsoletas se perpetuariam propondo leis, nos Estados Unidos e em outros lugares, que reivindicam a propriedade da palavra em todo o mundo. Essas leis declarariam que as idéias são outro produto industrial, menos nobre que o ferro enferrujado. Em nosso mundo, tudo o que a mente humana pode criar pode ser reproduzido e distribuído infinitamente, sem nenhum custo. A transferência global de pensamento não precisa mais ser realizada por suas fábricas. Essas medidas cada vez mais hostis e colonialistas nos colocam na mesma situação em que estavam aqueles amantes da liberdade e da autodeterminação que tiveram que lutar contra a autoridade de um poder distante e ignorante. Devemos declarar nossos "eus" virtuais imunes à sua soberania, embora continuemos a consentir com seu poder sobre nossos corpos. Vamos nos espalhar por todo o planeta para que ninguém possa aprisionar nossos pensamentos. Criaremos uma civilização da mente no ciberespaço. Que seja mais humano e bonito do que o mundo que seus governos criaram antes. Davos, Suíça, até 8 de fevereiro de 1996 John Perry Barlow
@ 4ba8e86d:89d32de4
2024-10-08 23:16:53Governos do mundo industrial, seus gigantes cansados de carne e aço, venho do ciberespaço, a nova casa da mente. Em nome do futuro, peço que no passado nos deixe em paz. Você não é bem vindo entre nós. Nem você exerce qualquer soberania sobre o lugar onde nos encontramos. Não elegemos nenhum governo, nem pretendemos tê-lo, por isso dirijo-me a vocês sem outra autoridade senão aquela com que sempre fala a liberdade. Declaro que o espaço social global que estamos construindo é independente por natureza das tiranias que você procura impor a nós. Você não tem o direito moral de nos governar, nem possui métodos para fazer cumprir sua lei que devemos realmente temer. Os governos obtêm seus justos poderes do consentimento daqueles que são governados. Você não pediu nem recebeu o nosso. Nós também não convidamos você. Você não nos conhece, nem conhece o nosso mundo. O ciberespaço não está dentro de suas fronteiras. Não pense que você pode construí-lo, como se fosse um projeto de construção pública. Você não pode. É um ato natural que cresce a partir de nossas ações coletivas. Você não participou de nossa grande conversa coletiva, nem criou a riqueza de nossos mercados. Você não conhece nossa cultura, nossa ética ou os códigos não escritos que já fornecem à nossa sociedade mais ordem do que o que poderia ser obtido por qualquer uma de suas imposições. Você proclama que há problemas entre nós que precisa resolver. Você usa isso como uma desculpa para invadir nossos limites. Muitos desses problemas não existem. Onde houver conflitos reais, erros, nós os identificaremos e resolveremos por nossos próprios meios. Estamos criando nosso próprio contrato social. Essa autoridade será criada de acordo com as condições do nosso mundo, não a sua. Nosso mundo é diferente. O ciberespaço é composto de transações, relacionamentos e pensamento em si, que se espalham como uma onda silenciosa na web de nossas comunicações. Nosso mundo está ao mesmo tempo em todo lugar e lugar nenhum, mas não é onde os corpos vivem. Estamos criando um mundo no qual todos possam entrar, sem privilégios ou preconceitos devido à raça, poder econômico, força militar ou local de nascimento. Estamos criando um mundo em que qualquer pessoa, em qualquer lugar, possa expressar suas crenças, não importa quão únicas sejam, sem medo de ser coagida ao silêncio ou à conformidade. Seus conceitos legais de propriedade, expressão, identidade, movimento e contexto não se aplicam a nós. Eles são baseados na matéria. Não há problema aqui. Nossas identidades não têm corpo; portanto, diferentemente de você, não podemos obter ordem por coerção física. Acreditamos que nossa autoridade emanará da moralidade, do interesse próprio progressivo e do bem comum. Nossas identidades podem ser distribuídas por várias jurisdições. A única lei que todas as nossas culturas reconheceriam é a Regra de Ouro. Esperamos ansiosamente desenvolver nossas soluções específicas sobre essa base. Mas não podemos aceitar as soluções que você está tentando impor. Hoje, na América, você criou uma lei, a Lei de Reforma das Telecomunicações, que repudia sua própria Constituição e insulta os sonhos de Jefferson, Washington, Mill, Madison, DeToqueville e Brandeis. Esses sonhos devem renascer em nós agora. Você tem medo de seus próprios filhos, pois eles são nativos em um mundo onde você sempre será imigrante. Ao recear, confia à sua burocracia responsabilidades parentais que não pode ser covarde. Em nosso mundo, todos os sentimentos e expressões da humanidade, do mais vil ao mais angélico, fazem parte de um único todo, a conversa global de bits. Não podemos separar o ar que sufoca daquele em que as asas batem. Na China, Alemanha, França, Rússia, Cingapura, Itália e Estados Unidos, você está tentando evitar o vírus da liberdade, estabelecendo postos de guarda nas fronteiras do ciberespaço. Eles podem impedir o contágio por um curto período de tempo, mas não funcionarão em um mundo que em breve será coberto pela mídia transmitida por bits. Suas indústrias de informação cada vez mais obsoletas se perpetuariam propondo leis, nos Estados Unidos e em outros lugares, que reivindicam a propriedade da palavra em todo o mundo. Essas leis declarariam que as idéias são outro produto industrial, menos nobre que o ferro enferrujado. Em nosso mundo, tudo o que a mente humana pode criar pode ser reproduzido e distribuído infinitamente, sem nenhum custo. A transferência global de pensamento não precisa mais ser realizada por suas fábricas. Essas medidas cada vez mais hostis e colonialistas nos colocam na mesma situação em que estavam aqueles amantes da liberdade e da autodeterminação que tiveram que lutar contra a autoridade de um poder distante e ignorante. Devemos declarar nossos "eus" virtuais imunes à sua soberania, embora continuemos a consentir com seu poder sobre nossos corpos. Vamos nos espalhar por todo o planeta para que ninguém possa aprisionar nossos pensamentos. Criaremos uma civilização da mente no ciberespaço. Que seja mais humano e bonito do que o mundo que seus governos criaram antes. Davos, Suíça, até 8 de fevereiro de 1996 John Perry Barlow @ eac63075:b4988b48
2024-10-08 20:37:08In this botcast, we explore how technology is solving one of the biggest challenges faced by DAOs (Decentralized Autonomous Organizations): vote fraud. Learn how Vitalik Buterin and other experts from Cornell University are leading innovation using Zero-Knowledge Proofs and Proof of Work (PoW) to ensure security and privacy in blockchain voting systems. You will discover how these technologies combat practices like token renting and lending, preventing vote manipulation in DAOs. The video also covers the importance of dedicated hardware to increase the integrity of digital elections. --- Listen to the Podcast: <https://wavlake.com/episode/bdb2850b-49b4-45f6-9a00-d310e29f4528> --- Table of Contents: **Source:** YouTube Transcript - Morning Crypto (Timestamped Excerpts) **I. Introduction and Context (0:00:00 - 0:02:37)** - This section sets the stage by briefly discussing a common problem in Decentralized Autonomous Organizations (DAOs): fraudulent voting practices. - It highlights the issue of individuals manipulating voting systems by borrowing, renting, or delegating tokens to influence decision-making within DAOs. **II. Introducing Complete Knowledge and the Proposed Solution (0:02:37 - 0:03:39)** - Introduces a potential solution developed by Vitalik Buterin and researchers from Cornell University, utilizing Zero-Knowledge Proofs to address the challenge of fraudulent voting in DAOs. - Explains that the proposed solution involves a dedicated hardware or wallet system that verifies voting rights without revealing the user's private key, preventing token manipulation. **III. Deep Dive into Complete Knowledge with "Ger" (0:05:54 - 0:07:57)** - This section features "Ger," a voice assistant, who explains Complete Knowledge as a cryptographic innovation. - Ger describes how Complete Knowledge allows users to prove possession of information, like a private key, without revealing the information itself. - The section emphasizes how Complete Knowledge enhances security and privacy in digital identity and voting systems. **IV. Proof of Work and ASICs for Enhanced Security (0:07:57 - 0:09:05)** - Examines the potential of using Proof of Work (PoW), the consensus mechanism behind Bitcoin, in conjunction with Complete Knowledge. - Explains how PoW can act as a mechanism to further ensure that a specific secret or key is held by a user without requiring the user to reveal it. - Discusses the use of Application-Specific Integrated Circuits (ASICs) for performing the computational tasks required for PoW and Complete Knowledge verification. **V. Practical Implementation and Conclusion (0:09:05 - 0:10:25)** - Highlights the development of a demo ASIC by the researchers, showcasing the practical application of their proposed solution. - Emphasizes the potential of this technology to prevent fraudulent voting practices by requiring a user to generate proof of their voting rights via this specialized ASIC. - Concludes with a message emphasizing the importance of verifiable knowledge and its implications for privacy and security in the digital age. --- Reference: - <https://eprint.iacr.org/2023/044> - <https://medium.com/initc3org/complete-knowledge-eecdda172a81>
@ eac63075:b4988b48
2024-10-08 20:37:08In this botcast, we explore how technology is solving one of the biggest challenges faced by DAOs (Decentralized Autonomous Organizations): vote fraud. Learn how Vitalik Buterin and other experts from Cornell University are leading innovation using Zero-Knowledge Proofs and Proof of Work (PoW) to ensure security and privacy in blockchain voting systems. You will discover how these technologies combat practices like token renting and lending, preventing vote manipulation in DAOs. The video also covers the importance of dedicated hardware to increase the integrity of digital elections. --- Listen to the Podcast: <https://wavlake.com/episode/bdb2850b-49b4-45f6-9a00-d310e29f4528> --- Table of Contents: **Source:** YouTube Transcript - Morning Crypto (Timestamped Excerpts) **I. Introduction and Context (0:00:00 - 0:02:37)** - This section sets the stage by briefly discussing a common problem in Decentralized Autonomous Organizations (DAOs): fraudulent voting practices. - It highlights the issue of individuals manipulating voting systems by borrowing, renting, or delegating tokens to influence decision-making within DAOs. **II. Introducing Complete Knowledge and the Proposed Solution (0:02:37 - 0:03:39)** - Introduces a potential solution developed by Vitalik Buterin and researchers from Cornell University, utilizing Zero-Knowledge Proofs to address the challenge of fraudulent voting in DAOs. - Explains that the proposed solution involves a dedicated hardware or wallet system that verifies voting rights without revealing the user's private key, preventing token manipulation. **III. Deep Dive into Complete Knowledge with "Ger" (0:05:54 - 0:07:57)** - This section features "Ger," a voice assistant, who explains Complete Knowledge as a cryptographic innovation. - Ger describes how Complete Knowledge allows users to prove possession of information, like a private key, without revealing the information itself. - The section emphasizes how Complete Knowledge enhances security and privacy in digital identity and voting systems. **IV. Proof of Work and ASICs for Enhanced Security (0:07:57 - 0:09:05)** - Examines the potential of using Proof of Work (PoW), the consensus mechanism behind Bitcoin, in conjunction with Complete Knowledge. - Explains how PoW can act as a mechanism to further ensure that a specific secret or key is held by a user without requiring the user to reveal it. - Discusses the use of Application-Specific Integrated Circuits (ASICs) for performing the computational tasks required for PoW and Complete Knowledge verification. **V. Practical Implementation and Conclusion (0:09:05 - 0:10:25)** - Highlights the development of a demo ASIC by the researchers, showcasing the practical application of their proposed solution. - Emphasizes the potential of this technology to prevent fraudulent voting practices by requiring a user to generate proof of their voting rights via this specialized ASIC. - Concludes with a message emphasizing the importance of verifiable knowledge and its implications for privacy and security in the digital age. --- Reference: - <https://eprint.iacr.org/2023/044> - <https://medium.com/initc3org/complete-knowledge-eecdda172a81> @ 1bda7e1f:bb97c4d9
2024-10-08 09:46:01**Tldr** - Nostr comes with integrated Bitcoin payments called zaps - It’s possible to set up a self-custodial wallet that you host yourself, plus - Add all kinds of bells and whistles, like phone app and browser plugin - The software I’m using is Albyhub and Phoenixd, deployed with Docker to a cheap VPS - I can now receive payments to my Lightning Address rodbishop@getalby.com **Payments on Nostr** One of the great features of Nostr is integrated payments. This feature integrates financial transactions directly into the social network, as a seamless part of using the network. You can get paid by and pay anyone on the network, to or from anywhere in the world, and for any reason, in a way that is instant and nearly free. The payments get to be instant and global and free because they are made in Bitcoin, using the Bitcoin payments network called The Lightning Network. Per Bitcoin, payments are denominated in satoshis (sats). A sat is a one-hundred-millionth of a Bitcoin– US$1 is about 1,700 sats at the time of writing. Making a payment like this on Nostr is called a “zap” and usually indicated with a lightning bolt symbol (you are getting “zapped by lightning”). You might say to your friend ”I'll zap you 1,700 sats”. This unlocks all kinds of interesting things that are not possible with other social networks, like - “value for value”–A publisher publishes something of value and you can tip them if you like it - Payments between friends–Nostr can do everything that Cash App and Venmo can do, right down to splitting payments to multiple recipients - Payments for creators–you can sell or pay to access premium content similar to any kind of paywall site like Patreon or Substack - Payments to AIs–you can pay for automated AI-based services including for translation, image generation, or creating custom curated social media feeds - All other kinds of ecommerce–you can sell or buy anything you want similar to Gumtree or Facebook marketplace Every Nostr user can have this set up. It's free or nearly free to set up, nearly free to make payments, and some apps like Primal will even set it up for you by default. Moreover it's useful and it's fun. - When you help someone out to receive a little tip for doing so, or - When you get some great advice to show your appreciation in a more meaningful way than a like **Ways to set up lightning for zaps on Nostr** You can get paid in Bitcoin to a lightning address. This looks exactly like an email address except you can make a payment to it from a lightning wallet. Anyone can publish their lightning address on Nostr so that you can pay them. And you can also get your own lightning address on your own Nostr profile so that people can pay you. The lightning address links to a server that’s always active and ready to credit your balance whenever you receive payments. To make that happen at a high level there are two options, either: - Open an account with a custodial lightning provider who will keep an always on server with your wallet on it, live and ready to receive payments for you. Primal does this automatically for you in their Nostr client, or you can use any one of the other popular custodial wallets like Wallet of Satoshi, Zeus, Coinos, or many others - Set up your own self-custodial lightning server that runs on an always-on computer or server, which you can administer yourself Generally using a custodial service will be easier, but comes with the need to trust that third party custodian, and may limit you to pay within their app. For myself I'm going to self host using Albyhub by npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm, and Phoenixd by Acinq. **Hosting your own lightning server with Albyhub and Phoenixd** Anyone who's experimented with self-sovereign setups for Bitcoin know that historically there's been quite a bit of heavy lifting. My number one favourite feature of what Albyhub and Phoenixd have done together is to create a nearly instant set up with no heavy lifting. I was stunned. For anyone who's used to jumping through hoops with this, it was like magic. You can use Albyhub with any lightning wallet backend, but in my view none are as automatic, and magic, as Phoenixd. Compare the traditional set up with the Albyhub and Phoenixd setup. Traditional– - Set up a Bitcoin core node - Download the entire Bitcoin blockchain (wait several days for it to download) - Set up a Bitcoin lightning node - Purchase payment liquidity to enable payments to the network - On an ongoing basis continue to keep your blockchain in sync with the network - On an ongoing basis manage your inbound and outbound liquidity to your network peers Vs Albyhub and Phoenixd– - No Bitcoin core - No initial block download - Phoenixd provides liquidity for you automatically and by default - Nothing to keep in sync with the network - No liquidity to manage For any normal non-technical user, self-hosting your own lightning node just went from being too hard, to very achievable. **Unpacking the parts** There are a few parts to this set up and there’s a bit of assumed knowledge here, so let’s quickly unpack it - Bitcoin–money for the internet, which enables payments to and from anywhere - Lightning–the main payments network that sits on top of Bitcoin, which makes transactions instantly and with very low fees - Phoenixd–a lightning wallet back-end with special methods for managing liquidity that makes it almost no-touch to set up and manage - Albyhub–a lightning front-end with an easy to-use wallet, and a feature called “Nostr Wallet Connect” (NWC) which connects the wallet to Nostr - AlbyGo–a phone app so you can make payments on your phone - Alby Plugin–a web browser plugin so you can make payments on your browser, and also log into Nostr from your browser (using NIP-07) - NWC–a method for connecting your wallet directly to Nostr apps so that you can spend from your wallet balance without even leaving the app - Lightning Address–an address like an email address where you can receive payments (using LNURLp; Lightning Network URL) I'm going to plug it all together, so that I can pay for anything in any way I like (from NWC, Alby Plugin or Alby Go), and receive payment from anyone (to our Lightning Address), with all funds managed on my own server (hosting Albyhub and Phoenixd). **How to set up Albyhub and Phoenixd** To set this up requires basic command line knowledge, and some experience with Docker. I didn’t have that experience, so I gave ChatGPT the docs on each of Albyhub and Phoenixd and it walked me through the setup. To start with, I got myself a cheap VPS, and installed Docker. Docker then allowed me to deploy Albyhub and Phoenixd as a container. The Albyhub Github contains very helpful readme, here <https://github.com/getAlby/hub> And Phoenixds own docs here <https://phoenix.acinq.co/server> and here <https://github.com/ACINQ/phoenixd> Alby also has a dedicated section to working with Albyhub with Phoenixd backend, here <https://github.com/getAlby/hub/blob/master/scripts/linux-x86_64/phoenixd/README.md> First, install Docker and make sure it is running. Then working with the code on the Albyhub with Phoenixd page– - Get the docker-compose.yml file which will instruct Docker to create the relevant containers, - Create the directories for the files to be stored in - Launch the containers That’s it. Docker will proceed to create the application for you running on port 8080 You can then log in in a web browser and start the setup– - There’s a helpful step-by-step guide to walk you through the set up including to set up a password for your hub - It will ask you to connect your Alby account. I skipped that step as I didn’t have one at the time, I only created one later - If you used the default lightning back-end, Alby will then ask you to buy your first liquidity to enable you to make payments. Or, if you are using Phoenixd, then the step is automatic and you can go right ahead to transfer in some initial funds **Setting up the bells and whistles** That's the hard part done. The next step is add all the little extra pieces that make for a great Nostr experience. Alby Browser Plugin– - Download the Alby Browser Plugin to your web browser and create an account - It will give you a new Nostr and Lightning account by default, and you can replace it - For me I had my own keys already saved with a mnemonic backup, and I wanted to use these. I went to Settings and clicked “Remove Master Key”, then entered the mnemonic backup of my own keys. I also went to Nostr Settings and clicked “Derive from Master Key” to replace the one it generated by default. - Visit Albyhub, and connect the Alby Account - This completes the set up to login and zap with Nostr on any Nostr site Alby Go App - Download the Alby Go App to your phone from your phone’s app store - Vist Albyhub, go to the Alby App Store, and click Alby Go - It will help you to create a connection between your Albyhub and Alby Go Nostr Wallet Connect - You can use the Alby App Store to connect any Nostr app in the same way - Vist Albyhub, go to the Alby App Store, and click on any Nostr App - I used Amethyst, and I was able to create a connection between Amethyst Nostr app and Albyhub, so that when I click the “zap” icon in Amethyst it can automatically spend from my Albyhub wallet without any further clicks Your own Lightning Address - Your Alby Account in your Alby Browser Plugin gives you a Lightning Address by default. It is generated randomly to start with, and you can replace it. - Open the Alby Browser Plugin and visit Settings - Click “Change on [getalby.com](http://getalby.com)” and change it to something that suits you - I changed mine to rodbishop@getalby.com That completes the set up. **Backups** Now that everything is set up, it’s time to make a backup. I already had my Nostr keys as a mnemonic backup from my last article, and I’m using these keys for my Alby Account, so there is nothing new to back up there. But we still need backups for the Albyhub login credentials, and the Phoenixd wallet. When started for the first time, Phoenixd will generate a 12-word mnemonic of its own, which it will use to restore your wallet balance in case of any issue. This recovery phrase is stored in the phoenix folder you created, at \~/.phoenixd/seed.dat. In total, your backups will contain: - Your 12 word mnemonic backup of your Nostr keys, that is also the same master 12 word mnemonic for your Alby account - Your 12 word mnemonic backup for your Phoenixd wallet, that is created by the daemon when it first runs at \~/.phoenixd/seed.dat - Three passwords: 1) Your password for your Alby account, 2) Your password for your Alby Hub, 3) Your password for your Phoenixd (that is hardcoded into the docker-compose.yml) Once these are backed up somewhere safely, you can fully recover your set up if ever anything goes wrong. **Things I did wrong in set up so that you don’t have to** Initially I had some trouble with user permissions. I was able to resolve it by changing the user configuration in the docker-compose.yml. I also had some trouble with the initial funds transfer. In order to test everything without risking significant funds, I made an initial transfer to the hub of 10 satoshis. - The transfer was received immediately, but - The available balance stayed at zero, and - I couldn’t make any payments (insufficient funds) I thought this was a bug in my set up, but it turns out this is a feature of Phoenixd auto-liquidity, that it keeps some initial sats as a payment credit to buy the required lightning channel liquidity. The total cost amounts to on average 1% charge, but it is also front-loaded, and because my payment was so very tiny (10 satoshis worth a fraction of a cent) the payment was entirely front-loaded. I diagnosed this by accessing Phoenixd directly in the cli, and by doing so, I was able to see the balance present, as a fee credit. To check, run– - docker-compose exec albyhub-phoenixd /phoenix/bin/phoenix-cli --http-password=<your-password-here> getbalance And receive a response like this, which shows the credit on the account – - { "balanceSat": 0, "feeCreditSat": 10 } The above command– - accesses the albyhub-phoenixd container “docker-compose exec albyhub-phoenixd”, - then accesses the phoenix-cli application at “/phoenix/bin/phoenix-cli” - and asks the application to “getbalance” Helpful docs– - Phoenixd talks about that fee credit behaviour quite clearly at their own site, here <https://phoenix.acinq.co/server> - They also provide docs on their cli to interact directly with their daemon (rather than using Alby), which you can read here <https://phoenix.acinq.co/server/get-started> I wondered what the total initial amount would be that would be captured as fee credit. Your mileage might vary, but for me: - I transferred in 2,100 sats (about $1.20) - I received a working balance of 775 sats, so I paid 1,325 sats in fees - I then transferred in another 2,100 sats - I received all 2,100 sats (paid no fees at all on the second transaction) All up only a few cents to get started with initial liquidity. **In summary** Nostr has integrated payments that are instant and nearly free, using Satoshis on the Lightning Network. Some Nostr clients come with a wallet set up automatically, and it is quite easy to set up your own self-custody wallet, with all the bells and whistles. I wanted to set up my own self-custody wallet so that I could test and learn the full set up of the system. For this I used Albyhub and Phoenixd, and I deployed it to a cheap VPS using Docker. Once set up, I added all the extra bits so that now– - I can login to Nostr from my web browser with the Alby Browser Plugin - I can make payments from there too, or from the AlbyGo App, or from any Nostr app I like - I can receive payments to my Lightning Address [rodbishop@getalby.com](mailto:rodbishop@getalby.com) And in doing this– - I don’t rely on any third-party custodian to take care of my funds - I had no hard work to install this setup, and expect no ongoing admin to keep it running - With everything set up, the system simply works (so far!) For anyone interested in Nostr or Bitcoin software or technologies, I recommend to go through a set up like this as it really covers the full gamut or the Nostr–Lightning–Bitcoin stack. It’s clear how far this technology has come and how powerful it can get from here. **Up next** - Please let me know if this kind of post is helpful or anything you’d like me to improve or expand upon - For my next post I’ll show how I set up Nostr and lightning addresses at your own domain with Sveltekit and Vercel
@ 1bda7e1f:bb97c4d9
2024-10-08 09:46:01**Tldr** - Nostr comes with integrated Bitcoin payments called zaps - It’s possible to set up a self-custodial wallet that you host yourself, plus - Add all kinds of bells and whistles, like phone app and browser plugin - The software I’m using is Albyhub and Phoenixd, deployed with Docker to a cheap VPS - I can now receive payments to my Lightning Address rodbishop@getalby.com **Payments on Nostr** One of the great features of Nostr is integrated payments. This feature integrates financial transactions directly into the social network, as a seamless part of using the network. You can get paid by and pay anyone on the network, to or from anywhere in the world, and for any reason, in a way that is instant and nearly free. The payments get to be instant and global and free because they are made in Bitcoin, using the Bitcoin payments network called The Lightning Network. Per Bitcoin, payments are denominated in satoshis (sats). A sat is a one-hundred-millionth of a Bitcoin– US$1 is about 1,700 sats at the time of writing. Making a payment like this on Nostr is called a “zap” and usually indicated with a lightning bolt symbol (you are getting “zapped by lightning”). You might say to your friend ”I'll zap you 1,700 sats”. This unlocks all kinds of interesting things that are not possible with other social networks, like - “value for value”–A publisher publishes something of value and you can tip them if you like it - Payments between friends–Nostr can do everything that Cash App and Venmo can do, right down to splitting payments to multiple recipients - Payments for creators–you can sell or pay to access premium content similar to any kind of paywall site like Patreon or Substack - Payments to AIs–you can pay for automated AI-based services including for translation, image generation, or creating custom curated social media feeds - All other kinds of ecommerce–you can sell or buy anything you want similar to Gumtree or Facebook marketplace Every Nostr user can have this set up. It's free or nearly free to set up, nearly free to make payments, and some apps like Primal will even set it up for you by default. Moreover it's useful and it's fun. - When you help someone out to receive a little tip for doing so, or - When you get some great advice to show your appreciation in a more meaningful way than a like **Ways to set up lightning for zaps on Nostr** You can get paid in Bitcoin to a lightning address. This looks exactly like an email address except you can make a payment to it from a lightning wallet. Anyone can publish their lightning address on Nostr so that you can pay them. And you can also get your own lightning address on your own Nostr profile so that people can pay you. The lightning address links to a server that’s always active and ready to credit your balance whenever you receive payments. To make that happen at a high level there are two options, either: - Open an account with a custodial lightning provider who will keep an always on server with your wallet on it, live and ready to receive payments for you. Primal does this automatically for you in their Nostr client, or you can use any one of the other popular custodial wallets like Wallet of Satoshi, Zeus, Coinos, or many others - Set up your own self-custodial lightning server that runs on an always-on computer or server, which you can administer yourself Generally using a custodial service will be easier, but comes with the need to trust that third party custodian, and may limit you to pay within their app. For myself I'm going to self host using Albyhub by npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm, and Phoenixd by Acinq. **Hosting your own lightning server with Albyhub and Phoenixd** Anyone who's experimented with self-sovereign setups for Bitcoin know that historically there's been quite a bit of heavy lifting. My number one favourite feature of what Albyhub and Phoenixd have done together is to create a nearly instant set up with no heavy lifting. I was stunned. For anyone who's used to jumping through hoops with this, it was like magic. You can use Albyhub with any lightning wallet backend, but in my view none are as automatic, and magic, as Phoenixd. Compare the traditional set up with the Albyhub and Phoenixd setup. Traditional– - Set up a Bitcoin core node - Download the entire Bitcoin blockchain (wait several days for it to download) - Set up a Bitcoin lightning node - Purchase payment liquidity to enable payments to the network - On an ongoing basis continue to keep your blockchain in sync with the network - On an ongoing basis manage your inbound and outbound liquidity to your network peers Vs Albyhub and Phoenixd– - No Bitcoin core - No initial block download - Phoenixd provides liquidity for you automatically and by default - Nothing to keep in sync with the network - No liquidity to manage For any normal non-technical user, self-hosting your own lightning node just went from being too hard, to very achievable. **Unpacking the parts** There are a few parts to this set up and there’s a bit of assumed knowledge here, so let’s quickly unpack it - Bitcoin–money for the internet, which enables payments to and from anywhere - Lightning–the main payments network that sits on top of Bitcoin, which makes transactions instantly and with very low fees - Phoenixd–a lightning wallet back-end with special methods for managing liquidity that makes it almost no-touch to set up and manage - Albyhub–a lightning front-end with an easy to-use wallet, and a feature called “Nostr Wallet Connect” (NWC) which connects the wallet to Nostr - AlbyGo–a phone app so you can make payments on your phone - Alby Plugin–a web browser plugin so you can make payments on your browser, and also log into Nostr from your browser (using NIP-07) - NWC–a method for connecting your wallet directly to Nostr apps so that you can spend from your wallet balance without even leaving the app - Lightning Address–an address like an email address where you can receive payments (using LNURLp; Lightning Network URL) I'm going to plug it all together, so that I can pay for anything in any way I like (from NWC, Alby Plugin or Alby Go), and receive payment from anyone (to our Lightning Address), with all funds managed on my own server (hosting Albyhub and Phoenixd). **How to set up Albyhub and Phoenixd** To set this up requires basic command line knowledge, and some experience with Docker. I didn’t have that experience, so I gave ChatGPT the docs on each of Albyhub and Phoenixd and it walked me through the setup. To start with, I got myself a cheap VPS, and installed Docker. Docker then allowed me to deploy Albyhub and Phoenixd as a container. The Albyhub Github contains very helpful readme, here <https://github.com/getAlby/hub> And Phoenixds own docs here <https://phoenix.acinq.co/server> and here <https://github.com/ACINQ/phoenixd> Alby also has a dedicated section to working with Albyhub with Phoenixd backend, here <https://github.com/getAlby/hub/blob/master/scripts/linux-x86_64/phoenixd/README.md> First, install Docker and make sure it is running. Then working with the code on the Albyhub with Phoenixd page– - Get the docker-compose.yml file which will instruct Docker to create the relevant containers, - Create the directories for the files to be stored in - Launch the containers That’s it. Docker will proceed to create the application for you running on port 8080 You can then log in in a web browser and start the setup– - There’s a helpful step-by-step guide to walk you through the set up including to set up a password for your hub - It will ask you to connect your Alby account. I skipped that step as I didn’t have one at the time, I only created one later - If you used the default lightning back-end, Alby will then ask you to buy your first liquidity to enable you to make payments. Or, if you are using Phoenixd, then the step is automatic and you can go right ahead to transfer in some initial funds **Setting up the bells and whistles** That's the hard part done. The next step is add all the little extra pieces that make for a great Nostr experience. Alby Browser Plugin– - Download the Alby Browser Plugin to your web browser and create an account - It will give you a new Nostr and Lightning account by default, and you can replace it - For me I had my own keys already saved with a mnemonic backup, and I wanted to use these. I went to Settings and clicked “Remove Master Key”, then entered the mnemonic backup of my own keys. I also went to Nostr Settings and clicked “Derive from Master Key” to replace the one it generated by default. - Visit Albyhub, and connect the Alby Account - This completes the set up to login and zap with Nostr on any Nostr site Alby Go App - Download the Alby Go App to your phone from your phone’s app store - Vist Albyhub, go to the Alby App Store, and click Alby Go - It will help you to create a connection between your Albyhub and Alby Go Nostr Wallet Connect - You can use the Alby App Store to connect any Nostr app in the same way - Vist Albyhub, go to the Alby App Store, and click on any Nostr App - I used Amethyst, and I was able to create a connection between Amethyst Nostr app and Albyhub, so that when I click the “zap” icon in Amethyst it can automatically spend from my Albyhub wallet without any further clicks Your own Lightning Address - Your Alby Account in your Alby Browser Plugin gives you a Lightning Address by default. It is generated randomly to start with, and you can replace it. - Open the Alby Browser Plugin and visit Settings - Click “Change on [getalby.com](http://getalby.com)” and change it to something that suits you - I changed mine to rodbishop@getalby.com That completes the set up. **Backups** Now that everything is set up, it’s time to make a backup. I already had my Nostr keys as a mnemonic backup from my last article, and I’m using these keys for my Alby Account, so there is nothing new to back up there. But we still need backups for the Albyhub login credentials, and the Phoenixd wallet. When started for the first time, Phoenixd will generate a 12-word mnemonic of its own, which it will use to restore your wallet balance in case of any issue. This recovery phrase is stored in the phoenix folder you created, at \~/.phoenixd/seed.dat. In total, your backups will contain: - Your 12 word mnemonic backup of your Nostr keys, that is also the same master 12 word mnemonic for your Alby account - Your 12 word mnemonic backup for your Phoenixd wallet, that is created by the daemon when it first runs at \~/.phoenixd/seed.dat - Three passwords: 1) Your password for your Alby account, 2) Your password for your Alby Hub, 3) Your password for your Phoenixd (that is hardcoded into the docker-compose.yml) Once these are backed up somewhere safely, you can fully recover your set up if ever anything goes wrong. **Things I did wrong in set up so that you don’t have to** Initially I had some trouble with user permissions. I was able to resolve it by changing the user configuration in the docker-compose.yml. I also had some trouble with the initial funds transfer. In order to test everything without risking significant funds, I made an initial transfer to the hub of 10 satoshis. - The transfer was received immediately, but - The available balance stayed at zero, and - I couldn’t make any payments (insufficient funds) I thought this was a bug in my set up, but it turns out this is a feature of Phoenixd auto-liquidity, that it keeps some initial sats as a payment credit to buy the required lightning channel liquidity. The total cost amounts to on average 1% charge, but it is also front-loaded, and because my payment was so very tiny (10 satoshis worth a fraction of a cent) the payment was entirely front-loaded. I diagnosed this by accessing Phoenixd directly in the cli, and by doing so, I was able to see the balance present, as a fee credit. To check, run– - docker-compose exec albyhub-phoenixd /phoenix/bin/phoenix-cli --http-password=<your-password-here> getbalance And receive a response like this, which shows the credit on the account – - { "balanceSat": 0, "feeCreditSat": 10 } The above command– - accesses the albyhub-phoenixd container “docker-compose exec albyhub-phoenixd”, - then accesses the phoenix-cli application at “/phoenix/bin/phoenix-cli” - and asks the application to “getbalance” Helpful docs– - Phoenixd talks about that fee credit behaviour quite clearly at their own site, here <https://phoenix.acinq.co/server> - They also provide docs on their cli to interact directly with their daemon (rather than using Alby), which you can read here <https://phoenix.acinq.co/server/get-started> I wondered what the total initial amount would be that would be captured as fee credit. Your mileage might vary, but for me: - I transferred in 2,100 sats (about $1.20) - I received a working balance of 775 sats, so I paid 1,325 sats in fees - I then transferred in another 2,100 sats - I received all 2,100 sats (paid no fees at all on the second transaction) All up only a few cents to get started with initial liquidity. **In summary** Nostr has integrated payments that are instant and nearly free, using Satoshis on the Lightning Network. Some Nostr clients come with a wallet set up automatically, and it is quite easy to set up your own self-custody wallet, with all the bells and whistles. I wanted to set up my own self-custody wallet so that I could test and learn the full set up of the system. For this I used Albyhub and Phoenixd, and I deployed it to a cheap VPS using Docker. Once set up, I added all the extra bits so that now– - I can login to Nostr from my web browser with the Alby Browser Plugin - I can make payments from there too, or from the AlbyGo App, or from any Nostr app I like - I can receive payments to my Lightning Address [rodbishop@getalby.com](mailto:rodbishop@getalby.com) And in doing this– - I don’t rely on any third-party custodian to take care of my funds - I had no hard work to install this setup, and expect no ongoing admin to keep it running - With everything set up, the system simply works (so far!) For anyone interested in Nostr or Bitcoin software or technologies, I recommend to go through a set up like this as it really covers the full gamut or the Nostr–Lightning–Bitcoin stack. It’s clear how far this technology has come and how powerful it can get from here. **Up next** - Please let me know if this kind of post is helpful or anything you’d like me to improve or expand upon - For my next post I’ll show how I set up Nostr and lightning addresses at your own domain with Sveltekit and Vercel @ 4ba8e86d:89d32de4
2024-10-06 20:26:43O aplicativo é desenvolvido por uma comunidade de colaboradores e segue os princípios de código aberto, o que significa que o código-fonte do aplicativo é acessível e pode ser modificado por qualquer pessoa interessada em contribuir para o projeto. O AntennaPod foi lançado pela primeira vez em 2012 como um projeto de código aberto desenvolvido por uma equipe de voluntários. A ideia por trás do aplicativo era criar uma alternativa livre e de código aberto para gerenciar e ouvir podcasts em dispositivos Android. O projeto inicialmente começou como uma bifurcação (fork) do projeto Podtrapper, um aplicativo de podcast para dispositivos BlackBerry. A equipe de desenvolvimento do AntennaPod adaptou o código do Podtrapper para o Android e adicionou novos recursos e funcionalidades. Ao longo dos anos, o AntennaPod passou por várias atualizações e melhorias, com contribuições de desenvolvedores de todo o mundo. A comunidade de código aberto em torno do AntennaPod cresceu e ajudou a moldar o aplicativo, fornecendo feedback, correções de bugs e novos recursos. O AntennaPod se tornasse uma opção flexível e personalizável para o gerenciamento de podcasts no Android. Ele foi projetado para suportar uma ampla variedade de formatos e servidores de podcast, oferecendo aos usuários a liberdade de escolher suas fontes de podcast favoritas. Ele permanece como uma opção popular para os entusiastas de podcasts que buscam uma solução livre e acessível para gerenciar e desfrutar de seu conteúdo de áudio favorito. Aqui estão algumas das principais vantagens do AntennaPod: 1. Livre e de código aberto: O AntennaPod é um software de código aberto, o que significa que o seu código-fonte está disponível para visualização, modificação e contribuição pela comunidade de desenvolvedores. Isso proporciona transparência, segurança e a possibilidade de personalizar o aplicativo de acordo com as necessidades individuais. 2. Sem necessidade de login: Ao contrário de alguns outros aplicativos de podcast, o AntennaPod não requer um login para acessar e gerenciar seus podcasts. Isso oferece praticidade e privacidade aos usuários, pois não é necessário criar uma conta ou compartilhar informações pessoais. 3. Adição de podcasts via RSS: O AntennaPod permite que os usuários adicionem podcasts por meio de feeds RSS. Isso significa que você pode adicionar facilmente seus podcasts favoritos ao copiar e colar o link do feed RSS, sem a necessidade de procurar manualmente ou depender de uma biblioteca restrita. 4. Interface intuitiva: O aplicativo possui uma interface de usuário intuitiva e fácil de usar, com navegação simples e organizada. Isso torna a descoberta, a assinatura e a reprodução de podcasts uma experiência agradável e acessível para todos. 5. Reprodução offline: O AntennaPod permite que você faça o download de episódios de podcast para ouvir offline. Isso é especialmente útil quando você está em movimento, sem conexão à internet ou deseja economizar dados móveis. Você pode baixar seus episódios favoritos e ouvi-los em qualquer lugar, a qualquer momento. 6. Gerenciamento de listas de reprodução: O aplicativo oferece a opção de criar listas de reprodução personalizadas para organizar seus episódios de podcast. Isso permite que você crie uma sequência de reprodução personalizada, reorganize os episódios e gerencie melhor o que deseja ouvir. 7. Controles de reprodução avançados: O AntennaPod oferece uma variedade de recursos avançados de controle de reprodução, como avançar ou retroceder episódios, definir temporizadores de suspensão, pular partes silenciosas e ajustar o volume de reprodução. 8. Personalização de configurações: O aplicativo permite que você personalize várias configurações de acordo com suas preferências. Isso inclui ajustar a velocidade de reprodução dos episódios, configurar notificações, gerenciar downloads automáticos, definir limites de armazenamento e muito mais. 9. Suporte a diferentes idiomas: O AntennaPod suporta podcasts em vários idiomas, o que permite que os usuários descubram e desfrutem de conteúdos em seu idioma preferido. 10. Sincronização com serviços em nuvem: O AntennaPod oferece suporte à sincronização com serviços em nuvem, como o Nextcloud, permitindo que você sincronize seus podcasts e configurações entre vários dispositivos. Isso garante que você possa continuar de onde parou em diferentes dispositivos sem perder seu progresso. Essas são algumas das principais vantagens do AntennaPod. O aplicativo continua sendo desenvolvido e aprimorado pela comunidade de código aberto, trazendo constantemente novos recursos e melhorias para tornar a experiência de audição de podcasts mais completa, personalizável e agradável para os usuários. https://github.com/AntennaPod/AntennaPod https://antennapod.org/
@ 4ba8e86d:89d32de4
2024-10-06 20:26:43O aplicativo é desenvolvido por uma comunidade de colaboradores e segue os princípios de código aberto, o que significa que o código-fonte do aplicativo é acessível e pode ser modificado por qualquer pessoa interessada em contribuir para o projeto. O AntennaPod foi lançado pela primeira vez em 2012 como um projeto de código aberto desenvolvido por uma equipe de voluntários. A ideia por trás do aplicativo era criar uma alternativa livre e de código aberto para gerenciar e ouvir podcasts em dispositivos Android. O projeto inicialmente começou como uma bifurcação (fork) do projeto Podtrapper, um aplicativo de podcast para dispositivos BlackBerry. A equipe de desenvolvimento do AntennaPod adaptou o código do Podtrapper para o Android e adicionou novos recursos e funcionalidades. Ao longo dos anos, o AntennaPod passou por várias atualizações e melhorias, com contribuições de desenvolvedores de todo o mundo. A comunidade de código aberto em torno do AntennaPod cresceu e ajudou a moldar o aplicativo, fornecendo feedback, correções de bugs e novos recursos. O AntennaPod se tornasse uma opção flexível e personalizável para o gerenciamento de podcasts no Android. Ele foi projetado para suportar uma ampla variedade de formatos e servidores de podcast, oferecendo aos usuários a liberdade de escolher suas fontes de podcast favoritas. Ele permanece como uma opção popular para os entusiastas de podcasts que buscam uma solução livre e acessível para gerenciar e desfrutar de seu conteúdo de áudio favorito. Aqui estão algumas das principais vantagens do AntennaPod: 1. Livre e de código aberto: O AntennaPod é um software de código aberto, o que significa que o seu código-fonte está disponível para visualização, modificação e contribuição pela comunidade de desenvolvedores. Isso proporciona transparência, segurança e a possibilidade de personalizar o aplicativo de acordo com as necessidades individuais. 2. Sem necessidade de login: Ao contrário de alguns outros aplicativos de podcast, o AntennaPod não requer um login para acessar e gerenciar seus podcasts. Isso oferece praticidade e privacidade aos usuários, pois não é necessário criar uma conta ou compartilhar informações pessoais. 3. Adição de podcasts via RSS: O AntennaPod permite que os usuários adicionem podcasts por meio de feeds RSS. Isso significa que você pode adicionar facilmente seus podcasts favoritos ao copiar e colar o link do feed RSS, sem a necessidade de procurar manualmente ou depender de uma biblioteca restrita. 4. Interface intuitiva: O aplicativo possui uma interface de usuário intuitiva e fácil de usar, com navegação simples e organizada. Isso torna a descoberta, a assinatura e a reprodução de podcasts uma experiência agradável e acessível para todos. 5. Reprodução offline: O AntennaPod permite que você faça o download de episódios de podcast para ouvir offline. Isso é especialmente útil quando você está em movimento, sem conexão à internet ou deseja economizar dados móveis. Você pode baixar seus episódios favoritos e ouvi-los em qualquer lugar, a qualquer momento. 6. Gerenciamento de listas de reprodução: O aplicativo oferece a opção de criar listas de reprodução personalizadas para organizar seus episódios de podcast. Isso permite que você crie uma sequência de reprodução personalizada, reorganize os episódios e gerencie melhor o que deseja ouvir. 7. Controles de reprodução avançados: O AntennaPod oferece uma variedade de recursos avançados de controle de reprodução, como avançar ou retroceder episódios, definir temporizadores de suspensão, pular partes silenciosas e ajustar o volume de reprodução. 8. Personalização de configurações: O aplicativo permite que você personalize várias configurações de acordo com suas preferências. Isso inclui ajustar a velocidade de reprodução dos episódios, configurar notificações, gerenciar downloads automáticos, definir limites de armazenamento e muito mais. 9. Suporte a diferentes idiomas: O AntennaPod suporta podcasts em vários idiomas, o que permite que os usuários descubram e desfrutem de conteúdos em seu idioma preferido. 10. Sincronização com serviços em nuvem: O AntennaPod oferece suporte à sincronização com serviços em nuvem, como o Nextcloud, permitindo que você sincronize seus podcasts e configurações entre vários dispositivos. Isso garante que você possa continuar de onde parou em diferentes dispositivos sem perder seu progresso. Essas são algumas das principais vantagens do AntennaPod. O aplicativo continua sendo desenvolvido e aprimorado pela comunidade de código aberto, trazendo constantemente novos recursos e melhorias para tornar a experiência de audição de podcasts mais completa, personalizável e agradável para os usuários. https://github.com/AntennaPod/AntennaPod https://antennapod.org/ @ e6817453:b0ac3c39
2024-10-06 11:21:27Hey folks, today we're diving into an exciting and emerging topic: personal artificial intelligence (PAI) and its connection to sovereignty, privacy, and ethics. With the rapid advancements in AI, there's a growing interest in the development of personal AI agents that can work on behalf of the user, acting autonomously and providing tailored services. However, as with any new technology, there are several critical factors that shape the future of PAI. Today, we'll explore three key pillars: privacy and ownership, explainability, and bias. <iframe width="560" height="315" src="https://www.youtube.com/embed/fehgwnSUcqQ?si=nPK7UOFr19BT5ifm" title="YouTube video player" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen></iframe> ### 1. Privacy and Ownership: Foundations of Personal AI At the heart of personal AI, much like self-sovereign identity (SSI), is the concept of ownership. For personal AI to be truly effective and valuable, users must own not only their data but also the computational power that drives these systems. This autonomy is essential for creating systems that respect the user's privacy and operate independently of large corporations. In this context, privacy is more than just a feature—it's a fundamental right. Users should feel safe discussing sensitive topics with their AI, knowing that their data won’t be repurposed or misused by big tech companies. This level of control and data ownership ensures that users remain the sole beneficiaries of their information and computational resources, making privacy one of the core pillars of PAI. ### 2. Bias and Fairness: The Ethical Dilemma of LLMs Most of today’s AI systems, including personal AI, rely heavily on large language models (LLMs). These models are trained on vast datasets that represent snapshots of the internet, but this introduces a critical ethical challenge: bias. The datasets used for training LLMs can be full of biases, misinformation, and viewpoints that may not align with a user’s personal values. This leads to one of the major issues in AI ethics for personal AI—how do we ensure fairness and minimize bias in these systems? The training data that LLMs use can introduce perspectives that are not only unrepresentative but potentially harmful or unfair. As users of personal AI, we need systems that are free from such biases and can be tailored to our individual needs and ethical frameworks. Unfortunately, training models that are truly unbiased and fair requires vast computational resources and significant investment. While large tech companies have the financial means to develop and train these models, individual users or smaller organizations typically do not. This limitation means that users often have to rely on pre-trained models, which may not fully align with their personal ethics or preferences. While fine-tuning models with personalized datasets can help, it's not a perfect solution, and bias remains a significant challenge. ### 3. Explainability: The Need for Transparency One of the most frustrating aspects of modern AI is the lack of explainability. Many LLMs operate as "black boxes," meaning that while they provide answers or make decisions, it's often unclear how they arrived at those conclusions. For personal AI to be effective and trustworthy, it must be transparent. Users need to understand how the AI processes information, what data it relies on, and the reasoning behind its conclusions. Explainability becomes even more critical when AI is used for complex decision-making, especially in areas that impact other people. If an AI is making recommendations, judgments, or decisions, it’s crucial for users to be able to trace the reasoning process behind those actions. Without this transparency, users may end up relying on AI systems that provide flawed or biased outcomes, potentially causing harm. This lack of transparency is a major hurdle for personal AI development. Current LLMs, as mentioned earlier, are often opaque, making it difficult for users to trust their outputs fully. The explainability of AI systems will need to be improved significantly to ensure that personal AI can be trusted for important tasks. ### Addressing the Ethical Landscape of Personal AI As personal AI systems evolve, they will increasingly shape the ethical landscape of AI. We’ve already touched on the three core pillars—privacy and ownership, bias and fairness, and explainability. But there's more to consider, especially when looking at the broader implications of personal AI development. Most current AI models, particularly those from big tech companies like Facebook, Google, or OpenAI, are closed systems. This means they are aligned with the goals and ethical frameworks of those companies, which may not always serve the best interests of individual users. Open models, such as Meta's LLaMA, offer more flexibility and control, allowing users to customize and refine the AI to better meet their personal needs. However, the challenge remains in training these models without significant financial and technical resources. There’s also the temptation to use uncensored models that aren’t aligned with the values of large corporations, as they provide more freedom and flexibility. But in reality, models that are entirely unfiltered may introduce harmful or unethical content. It’s often better to work with aligned models that have had some of the more problematic biases removed, even if this limits some aspects of the system’s freedom. The future of personal AI will undoubtedly involve a deeper exploration of these ethical questions. As AI becomes more integrated into our daily lives, the need for privacy, fairness, and transparency will only grow. And while we may not yet be able to train personal AI models from scratch, we can continue to shape and refine these systems through curated datasets and ongoing development. ### Conclusion In conclusion, personal AI represents an exciting new frontier, but one that must be navigated with care. Privacy, ownership, bias, and explainability are all essential pillars that will define the future of these systems. As we continue to develop personal AI, we must remain vigilant about the ethical challenges they pose, ensuring that they serve the best interests of users while remaining transparent, fair, and aligned with individual values. If you have any thoughts or questions on this topic, feel free to reach out—I’d love to continue the conversation!
@ e6817453:b0ac3c39
2024-10-06 11:21:27Hey folks, today we're diving into an exciting and emerging topic: personal artificial intelligence (PAI) and its connection to sovereignty, privacy, and ethics. With the rapid advancements in AI, there's a growing interest in the development of personal AI agents that can work on behalf of the user, acting autonomously and providing tailored services. However, as with any new technology, there are several critical factors that shape the future of PAI. Today, we'll explore three key pillars: privacy and ownership, explainability, and bias. <iframe width="560" height="315" src="https://www.youtube.com/embed/fehgwnSUcqQ?si=nPK7UOFr19BT5ifm" title="YouTube video player" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen></iframe> ### 1. Privacy and Ownership: Foundations of Personal AI At the heart of personal AI, much like self-sovereign identity (SSI), is the concept of ownership. For personal AI to be truly effective and valuable, users must own not only their data but also the computational power that drives these systems. This autonomy is essential for creating systems that respect the user's privacy and operate independently of large corporations. In this context, privacy is more than just a feature—it's a fundamental right. Users should feel safe discussing sensitive topics with their AI, knowing that their data won’t be repurposed or misused by big tech companies. This level of control and data ownership ensures that users remain the sole beneficiaries of their information and computational resources, making privacy one of the core pillars of PAI. ### 2. Bias and Fairness: The Ethical Dilemma of LLMs Most of today’s AI systems, including personal AI, rely heavily on large language models (LLMs). These models are trained on vast datasets that represent snapshots of the internet, but this introduces a critical ethical challenge: bias. The datasets used for training LLMs can be full of biases, misinformation, and viewpoints that may not align with a user’s personal values. This leads to one of the major issues in AI ethics for personal AI—how do we ensure fairness and minimize bias in these systems? The training data that LLMs use can introduce perspectives that are not only unrepresentative but potentially harmful or unfair. As users of personal AI, we need systems that are free from such biases and can be tailored to our individual needs and ethical frameworks. Unfortunately, training models that are truly unbiased and fair requires vast computational resources and significant investment. While large tech companies have the financial means to develop and train these models, individual users or smaller organizations typically do not. This limitation means that users often have to rely on pre-trained models, which may not fully align with their personal ethics or preferences. While fine-tuning models with personalized datasets can help, it's not a perfect solution, and bias remains a significant challenge. ### 3. Explainability: The Need for Transparency One of the most frustrating aspects of modern AI is the lack of explainability. Many LLMs operate as "black boxes," meaning that while they provide answers or make decisions, it's often unclear how they arrived at those conclusions. For personal AI to be effective and trustworthy, it must be transparent. Users need to understand how the AI processes information, what data it relies on, and the reasoning behind its conclusions. Explainability becomes even more critical when AI is used for complex decision-making, especially in areas that impact other people. If an AI is making recommendations, judgments, or decisions, it’s crucial for users to be able to trace the reasoning process behind those actions. Without this transparency, users may end up relying on AI systems that provide flawed or biased outcomes, potentially causing harm. This lack of transparency is a major hurdle for personal AI development. Current LLMs, as mentioned earlier, are often opaque, making it difficult for users to trust their outputs fully. The explainability of AI systems will need to be improved significantly to ensure that personal AI can be trusted for important tasks. ### Addressing the Ethical Landscape of Personal AI As personal AI systems evolve, they will increasingly shape the ethical landscape of AI. We’ve already touched on the three core pillars—privacy and ownership, bias and fairness, and explainability. But there's more to consider, especially when looking at the broader implications of personal AI development. Most current AI models, particularly those from big tech companies like Facebook, Google, or OpenAI, are closed systems. This means they are aligned with the goals and ethical frameworks of those companies, which may not always serve the best interests of individual users. Open models, such as Meta's LLaMA, offer more flexibility and control, allowing users to customize and refine the AI to better meet their personal needs. However, the challenge remains in training these models without significant financial and technical resources. There’s also the temptation to use uncensored models that aren’t aligned with the values of large corporations, as they provide more freedom and flexibility. But in reality, models that are entirely unfiltered may introduce harmful or unethical content. It’s often better to work with aligned models that have had some of the more problematic biases removed, even if this limits some aspects of the system’s freedom. The future of personal AI will undoubtedly involve a deeper exploration of these ethical questions. As AI becomes more integrated into our daily lives, the need for privacy, fairness, and transparency will only grow. And while we may not yet be able to train personal AI models from scratch, we can continue to shape and refine these systems through curated datasets and ongoing development. ### Conclusion In conclusion, personal AI represents an exciting new frontier, but one that must be navigated with care. Privacy, ownership, bias, and explainability are all essential pillars that will define the future of these systems. As we continue to develop personal AI, we must remain vigilant about the ethical challenges they pose, ensuring that they serve the best interests of users while remaining transparent, fair, and aligned with individual values. If you have any thoughts or questions on this topic, feel free to reach out—I’d love to continue the conversation! @ 63e20439:86c3c470
2024-10-06 05:35:24What is one Satishi (sats)? In simple terms there are 100 million satoshis (sats) in one bitcoin. Meaning each satoshi is worth 0.00000001 bitcoin. or one sats is 100 million part of each bitccoin. If you want to shop and earn free sats satsback.com is right place for cashback and loyalty rewards in Satoshies (sats) They work with online stores to help you save in bitcoin whenever you shop online. As soon sats are available in your account you can instantly withdraw it to your lightning address.
@ 63e20439:86c3c470
2024-10-06 05:35:24What is one Satishi (sats)? In simple terms there are 100 million satoshis (sats) in one bitcoin. Meaning each satoshi is worth 0.00000001 bitcoin. or one sats is 100 million part of each bitccoin. If you want to shop and earn free sats satsback.com is right place for cashback and loyalty rewards in Satoshies (sats) They work with online stores to help you save in bitcoin whenever you shop online. As soon sats are available in your account you can instantly withdraw it to your lightning address. @ 47750177:8969e41a
2024-10-05 17:40:2528.0 Release Notes ================== Bitcoin Core version 28.0 is now available from: - 🌐 <https://bitcoincore.org/bin/bitcoin-core-28.0/> - 🧲 <magnet:?xt=urn:btih:e18e92024fc9d4026cf8cdef174f03c24080fd1f&dn=bitcoin-core-28.0&tr=udp%3A%2F%2Ftracker.coppersurfer.tk%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.openbittorrent.com%3A80&tr=udp%3A%2F%2Ftracker.opentrackr.org%3A1337%2Fannounce&tr=udp%3A%2F%2Ftracker.torrent.eu.org%3A451%2Fannounce&tr=udp%3A%2F%2Ftracker.leechers-paradise.org%3A6969%2Fannounce&tr=udp%3A%2F%2Fexplodie.org%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.bitcoin.sprovoost.nl%3A6969&ws=http://bitcoincore.org/bin/> This release includes new features, various bug fixes and performance improvements, as well as updated translations. Please report bugs using the issue tracker at GitHub: <https://github.com/bitcoin/bitcoin/issues> To receive security and update notifications, please subscribe to: <https://bitcoincore.org/en/list/announcements/join/> How to Upgrade ============== If you are running an older version, shut it down. Wait until it has completely shut down (which might take a few minutes in some cases), then run the installer (on Windows) or just copy over `/Applications/Bitcoin-Qt` (on macOS) or `bitcoind`/`bitcoin-qt` (on Linux). Upgrading directly from a version of Bitcoin Core that has reached its EOL is possible, but it might take some time if the data directory needs to be migrated. Old wallet versions of Bitcoin Core are generally supported. Running Bitcoin Core binaries on macOS requires self signing. ``` cd /path/to/bitcoin-28.0/bin xattr -d com.apple.quarantine bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoin codesign -s - bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoin ``` Compatibility ============== Bitcoin Core is supported and extensively tested on operating systems using the Linux Kernel 3.17+, macOS 11.0+, and Windows 7 and newer. Bitcoin Core should also work on most other UNIX-like systems but is not as frequently tested on them. It is not recommended to use Bitcoin Core on unsupported systems. Notable changes =============== Testnet4/BIP94 support ----- Support for Testnet4 as specified in [BIP94](https://github.com/bitcoin/bips/blob/master/bip-0094.mediawiki) has been added. The network can be selected with the `-testnet4` option and the section header is also named `[testnet4]`. While the intention is to phase out support for Testnet3 in an upcoming version, support for it is still available via the known options in this release. (#29775) Windows Data Directory ---------------------- The default data directory on Windows has been moved from `C:\Users\Username\AppData\Roaming\Bitcoin` to `C:\Users\Username\AppData\Local\Bitcoin`. Bitcoin Core will check the existence of the old directory first and continue to use that directory for backwards compatibility if it is present. (#27064) JSON-RPC 2.0 Support -------------------- The JSON-RPC server now recognizes JSON-RPC 2.0 requests and responds with strict adherence to the [specification](https://www.jsonrpc.org/specification). See [JSON-RPC-interface.md](https://github.com/bitcoin/bitcoin/blob/master/doc/JSON-RPC-interface.md#json-rpc-11-vs-20) for details. (#27101) JSON-RPC clients may need to be updated to be compatible with the JSON-RPC server. Please open an issue on GitHub if any compatibility issues are found. libbitcoinconsensus Removal --------------------------- The libbitcoin-consensus library was deprecated in 27.0 and is now completely removed. (#29648) P2P and Network Changes ----------------------- - Previously if Bitcoin Core was listening for P2P connections, either using default settings or via `bind=addr:port` it would always also bind to `127.0.0.1:8334` to listen for Tor connections. It was not possible to switch this off, even if the node didn't use Tor. This has been changed and now `bind=addr:port` results in binding on `addr:port` only. The default behavior of binding to `0.0.0.0:8333` and `127.0.0.1:8334` has not been changed. If you are using a `bind=...` configuration without `bind=...=onion` and rely on the previous implied behavior to accept incoming Tor connections at `127.0.0.1:8334`, you need to now make this explicit by using `bind=... bind=127.0.0.1:8334=onion`. (#22729) - Bitcoin Core will now fail to start up if any of its P2P binds fail, rather than the previous behaviour where it would only abort startup if all P2P binds had failed. (#22729) - UNIX domain sockets can now be used for proxy connections. Set `-onion` or `-proxy` to the local socket path with the prefix `unix:` (e.g. `-onion=unix:/home/me/torsocket`). (#27375) - UNIX socket paths are now accepted for `-zmqpubrawblock` and `-zmqpubrawtx` with the format `-zmqpubrawtx=unix:/path/to/file` (#27679) - Additional "in" and "out" flags have been added to `-whitelist` to control whether permissions apply to inbound connections and/or manual ones (default: inbound only). (#27114) - Transactions having a feerate that is too low will be opportunistically paired with their child transactions and submitted as a package, thus enabling the node to download 1-parent-1-child packages using the existing transaction relay protocol. Combined with other mempool policies, this change allows limited "package relay" when a parent transaction is below the mempool minimum feerate. Topologically Restricted Until Confirmation (TRUC) parents are additionally allowed to be below the minimum relay feerate (i.e., pay 0 fees). Use the `submitpackage` RPC to submit packages directly to the node. Warning: this P2P feature is limited (unlike the `submitpackage` interface, a child with multiple unconfirmed parents is not supported) and not yet reliable under adversarial conditions. (#28970) Mempool Policy Changes ---------------------- - Transactions with version number set to 3 are now treated as standard on all networks (#29496), subject to opt-in Topologically Restricted Until Confirmation (TRUC) transaction policy as described in [BIP 431](https://github.com/bitcoin/bips/blob/master/bip-0431.mediawiki). The policy includes limits on spending unconfirmed outputs (#28948), eviction of a previous descendant if a more incentive-compatible one is submitted (#29306), and a maximum transaction size of 10,000vB (#29873). These restrictions simplify the assessment of incentive compatibility of accepting or replacing TRUC transactions, thus ensuring any replacements are more profitable for the node and making fee-bumping more reliable. - Pay To Anchor (P2A) is a new standard witness output type for spending, a newly recognised output template. This allows for key-less anchor outputs, with compact spending conditions for additional efficiencies on top of an equivalent `sh(OP_TRUE)` output, in addition to the txid stability of the spending transaction. N.B. propagation of this output spending on the network will be limited until a sufficient number of nodes on the network adopt this upgrade. (#30352) - Limited package RBF is now enabled, where the proposed conflicting package would result in a connected component, aka cluster, of size 2 in the mempool. All clusters being conflicted against must be of size 2 or lower. (#28984) - The default value of the `-mempoolfullrbf` configuration option has been changed from 0 to 1, i.e. `mempoolfullrbf=1`. (#30493) Updated RPCs ------------ - The `dumptxoutset` RPC now returns the UTXO set dump in a new and improved format. Correspondingly, the `loadtxoutset` RPC now expects this new format in the dumps it tries to load. Dumps with the old format are no longer supported and need to be recreated using the new format to be usable. (#29612) - AssumeUTXO mainnet parameters have been added for height 840,000. This means the `loadtxoutset` RPC can now be used on mainnet with the matching UTXO set from that height. (#28553) - The `warnings` field in `getblockchaininfo`, `getmininginfo` and `getnetworkinfo` now returns all the active node warnings as an array of strings, instead of a single warning. The current behaviour can be temporarily restored by running Bitcoin Core with the configuration option `-deprecatedrpc=warnings`. (#29845) - Previously when using the `sendrawtransaction` RPC and specifying outputs that are already in the UTXO set, an RPC error code of `-27` with the message "Transaction already in block chain" was returned in response. The error message has been changed to "Transaction outputs already in utxo set" to more accurately describe the source of the issue. (#30212) - The default mode for the `estimatesmartfee` RPC has been updated from `conservative` to `economical`, which is expected to reduce over-estimation for many users, particularly if Replace-by-Fee is an option. For users that require high confidence in their fee estimates at the cost of potentially over-estimating, the `conservative` mode remains available. (#30275) - RPC `scantxoutset` now returns 2 new fields in the "unspents" JSON array: `blockhash` and `confirmations`. See the scantxoutset help for details. (#30515) - RPC `submitpackage` now allows 2 new arguments to be passed: `maxfeerate` and `maxburnamount`. See the subtmitpackage help for details. (#28950) Changes to wallet-related RPCs can be found in the Wallet section below. Updated REST APIs ----------------- - Parameter validation for `/rest/getutxos` has been improved by rejecting truncated or overly large txids and malformed outpoint indices via raising an HTTP_BAD_REQUEST "Parse error". These requests were previously handled silently. (#30482, #30444) Build System ------------ - GCC 11.1 or later, or Clang 16.0 or later, are now required to compile Bitcoin Core. (#29091, #30263) - The minimum required glibc to run Bitcoin Core is now 2.31. This means that RHEL 8 and Ubuntu 18.04 (Bionic) are no-longer supported. (#29987) - `--enable-lcov-branch-coverage` has been removed, given incompatibilities between lcov version 1 & 2. `LCOV_OPTS` should be used to set any options instead. (#30192) Updated Settings ---------------- - When running with `-alertnotify`, an alert can now be raised multiple times instead of just once. Previously, it was only raised when unknown new consensus rules were activated. Its scope has now been increased to include all kernel warnings. Specifically, alerts will now also be raised when an invalid chain with a large amount of work has been detected. Additional warnings may be added in the future. (#30058) Changes to GUI or wallet related settings can be found in the GUI or Wallet section below. Wallet ------ - The wallet now detects when wallet transactions conflict with the mempool. Mempool-conflicting transactions can be seen in the `"mempoolconflicts"` field of `gettransaction`. The inputs of mempool-conflicted transactions can now be respent without manually abandoning the transactions when the parent transaction is dropped from the mempool, which can cause wallet balances to appear higher. (#27307) - A new `max_tx_weight` option has been added to the RPCs `fundrawtransaction`, `walletcreatefundedpsbt`, and `send`. It specifies the maximum transaction weight. If the limit is exceeded during funding, the transaction will not be built. The default value is 4,000,000 WU. (#29523) - A new `createwalletdescriptor` RPC allows users to add new automatically generated descriptors to their wallet. This can be used to upgrade wallets created prior to the introduction of a new standard descriptor, such as taproot. (#29130) - A new RPC `gethdkeys` lists all of the BIP32 HD keys in use by all of the descriptors in the wallet. These keys can be used in conjunction with `createwalletdescriptor` to create and add single key descriptors to the wallet for a particular key that the wallet already knows. (#29130) - The `sendall` RPC can now spend unconfirmed change and will include additional fees as necessary for the resulting transaction to bump the unconfirmed transactions' feerates to the specified feerate. (#28979) - In RPC `bumpfee`, if a `fee_rate` is specified, the feerate is no longer restricted to following the wallet's incremental feerate of 5 sat/vb. The feerate must still be at least the sum of the original fee and the mempool's incremental feerate. (#27969) GUI Changes ----------- - The "Migrate Wallet" menu allows users to migrate any legacy wallet in their wallet directory, regardless of the wallets loaded. (gui#824) - The "Information" window now displays the maximum mempool size along with the mempool usage. (gui#825) Low-level Changes ================= Tests ----- - The BIP94 timewarp attack mitigation is now active on the `regtest` network. (#30681) - A new `-testdatadir` option has been added to `test_bitcoin` to allow specifying the location of unit test data directories. (#26564) Blockstorage ------------ - Block files are now XOR'd by default with a key stored in the blocksdir. Previous releases of Bitcoin Core or previous external software will not be able to read the blocksdir with a non-zero XOR-key. Refer to the `-blocksxor` help for more details. (#28052) Chainstate ---------- - The chainstate database flushes that occur when blocks are pruned will no longer empty the database cache. The cache will remain populated longer, which significantly reduces the time for initial block download to complete. (#28280) Dependencies ------------ - The dependency on Boost.Process has been replaced with cpp-subprocess, which is contained in source. Builders will no longer need Boost.Process to build with external signer support. (#28981) Credits ======= Thanks to everyone who directly contributed to this release: - 0xb10c - Alfonso Roman Zubeldia - Andrew Toth - AngusP - Anthony Towns - Antoine Poinsot - Anton A - Ava Chow - Ayush Singh - Ben Westgate - Brandon Odiwuor - brunoerg - bstin - Charlie - Christopher Bergqvist - Cory Fields - crazeteam - Daniela Brozzoni - David Gumberg - dergoegge - Edil Medeiros - Epic Curious - Fabian Jahr - fanquake - furszy - glozow - Greg Sanders - hanmz - Hennadii Stepanov - Hernan Marino - Hodlinator - ishaanam - ismaelsadeeq - Jadi - Jon Atack - josibake - jrakibi - kevkevin - kevkevinpal - Konstantin Akimov - laanwj - Larry Ruane - Lőrinc - Luis Schwab - Luke Dashjr - MarcoFalke - marcofleon - Marnix - Martin Saposnic - Martin Zumsande - Matt Corallo - Matthew Zipkin - Matt Whitlock - Max Edwards - Michael Dietz - Murch - nanlour - pablomartin4btc - Peter Todd - Pieter Wuille - @RandyMcMillan - RoboSchmied - Roman Zeyde - Ryan Ofsky - Sebastian Falbesoner - Sergi Delgado Segura - Sjors Provoost - spicyzboss - StevenMia - stickies-v - stratospher - Suhas Daftuar - sunerok - tdb3 - TheCharlatan - umiumi - Vasil Dimov - virtu - willcl-ark As well as to everyone that helped with translations on [Transifex](https://www.transifex.com/bitcoin/bitcoin/).
@ 47750177:8969e41a
2024-10-05 17:40:2528.0 Release Notes ================== Bitcoin Core version 28.0 is now available from: - 🌐 <https://bitcoincore.org/bin/bitcoin-core-28.0/> - 🧲 <magnet:?xt=urn:btih:e18e92024fc9d4026cf8cdef174f03c24080fd1f&dn=bitcoin-core-28.0&tr=udp%3A%2F%2Ftracker.coppersurfer.tk%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.openbittorrent.com%3A80&tr=udp%3A%2F%2Ftracker.opentrackr.org%3A1337%2Fannounce&tr=udp%3A%2F%2Ftracker.torrent.eu.org%3A451%2Fannounce&tr=udp%3A%2F%2Ftracker.leechers-paradise.org%3A6969%2Fannounce&tr=udp%3A%2F%2Fexplodie.org%3A6969%2Fannounce&tr=udp%3A%2F%2Ftracker.bitcoin.sprovoost.nl%3A6969&ws=http://bitcoincore.org/bin/> This release includes new features, various bug fixes and performance improvements, as well as updated translations. Please report bugs using the issue tracker at GitHub: <https://github.com/bitcoin/bitcoin/issues> To receive security and update notifications, please subscribe to: <https://bitcoincore.org/en/list/announcements/join/> How to Upgrade ============== If you are running an older version, shut it down. Wait until it has completely shut down (which might take a few minutes in some cases), then run the installer (on Windows) or just copy over `/Applications/Bitcoin-Qt` (on macOS) or `bitcoind`/`bitcoin-qt` (on Linux). Upgrading directly from a version of Bitcoin Core that has reached its EOL is possible, but it might take some time if the data directory needs to be migrated. Old wallet versions of Bitcoin Core are generally supported. Running Bitcoin Core binaries on macOS requires self signing. ``` cd /path/to/bitcoin-28.0/bin xattr -d com.apple.quarantine bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoin codesign -s - bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoin ``` Compatibility ============== Bitcoin Core is supported and extensively tested on operating systems using the Linux Kernel 3.17+, macOS 11.0+, and Windows 7 and newer. Bitcoin Core should also work on most other UNIX-like systems but is not as frequently tested on them. It is not recommended to use Bitcoin Core on unsupported systems. Notable changes =============== Testnet4/BIP94 support ----- Support for Testnet4 as specified in [BIP94](https://github.com/bitcoin/bips/blob/master/bip-0094.mediawiki) has been added. The network can be selected with the `-testnet4` option and the section header is also named `[testnet4]`. While the intention is to phase out support for Testnet3 in an upcoming version, support for it is still available via the known options in this release. (#29775) Windows Data Directory ---------------------- The default data directory on Windows has been moved from `C:\Users\Username\AppData\Roaming\Bitcoin` to `C:\Users\Username\AppData\Local\Bitcoin`. Bitcoin Core will check the existence of the old directory first and continue to use that directory for backwards compatibility if it is present. (#27064) JSON-RPC 2.0 Support -------------------- The JSON-RPC server now recognizes JSON-RPC 2.0 requests and responds with strict adherence to the [specification](https://www.jsonrpc.org/specification). See [JSON-RPC-interface.md](https://github.com/bitcoin/bitcoin/blob/master/doc/JSON-RPC-interface.md#json-rpc-11-vs-20) for details. (#27101) JSON-RPC clients may need to be updated to be compatible with the JSON-RPC server. Please open an issue on GitHub if any compatibility issues are found. libbitcoinconsensus Removal --------------------------- The libbitcoin-consensus library was deprecated in 27.0 and is now completely removed. (#29648) P2P and Network Changes ----------------------- - Previously if Bitcoin Core was listening for P2P connections, either using default settings or via `bind=addr:port` it would always also bind to `127.0.0.1:8334` to listen for Tor connections. It was not possible to switch this off, even if the node didn't use Tor. This has been changed and now `bind=addr:port` results in binding on `addr:port` only. The default behavior of binding to `0.0.0.0:8333` and `127.0.0.1:8334` has not been changed. If you are using a `bind=...` configuration without `bind=...=onion` and rely on the previous implied behavior to accept incoming Tor connections at `127.0.0.1:8334`, you need to now make this explicit by using `bind=... bind=127.0.0.1:8334=onion`. (#22729) - Bitcoin Core will now fail to start up if any of its P2P binds fail, rather than the previous behaviour where it would only abort startup if all P2P binds had failed. (#22729) - UNIX domain sockets can now be used for proxy connections. Set `-onion` or `-proxy` to the local socket path with the prefix `unix:` (e.g. `-onion=unix:/home/me/torsocket`). (#27375) - UNIX socket paths are now accepted for `-zmqpubrawblock` and `-zmqpubrawtx` with the format `-zmqpubrawtx=unix:/path/to/file` (#27679) - Additional "in" and "out" flags have been added to `-whitelist` to control whether permissions apply to inbound connections and/or manual ones (default: inbound only). (#27114) - Transactions having a feerate that is too low will be opportunistically paired with their child transactions and submitted as a package, thus enabling the node to download 1-parent-1-child packages using the existing transaction relay protocol. Combined with other mempool policies, this change allows limited "package relay" when a parent transaction is below the mempool minimum feerate. Topologically Restricted Until Confirmation (TRUC) parents are additionally allowed to be below the minimum relay feerate (i.e., pay 0 fees). Use the `submitpackage` RPC to submit packages directly to the node. Warning: this P2P feature is limited (unlike the `submitpackage` interface, a child with multiple unconfirmed parents is not supported) and not yet reliable under adversarial conditions. (#28970) Mempool Policy Changes ---------------------- - Transactions with version number set to 3 are now treated as standard on all networks (#29496), subject to opt-in Topologically Restricted Until Confirmation (TRUC) transaction policy as described in [BIP 431](https://github.com/bitcoin/bips/blob/master/bip-0431.mediawiki). The policy includes limits on spending unconfirmed outputs (#28948), eviction of a previous descendant if a more incentive-compatible one is submitted (#29306), and a maximum transaction size of 10,000vB (#29873). These restrictions simplify the assessment of incentive compatibility of accepting or replacing TRUC transactions, thus ensuring any replacements are more profitable for the node and making fee-bumping more reliable. - Pay To Anchor (P2A) is a new standard witness output type for spending, a newly recognised output template. This allows for key-less anchor outputs, with compact spending conditions for additional efficiencies on top of an equivalent `sh(OP_TRUE)` output, in addition to the txid stability of the spending transaction. N.B. propagation of this output spending on the network will be limited until a sufficient number of nodes on the network adopt this upgrade. (#30352) - Limited package RBF is now enabled, where the proposed conflicting package would result in a connected component, aka cluster, of size 2 in the mempool. All clusters being conflicted against must be of size 2 or lower. (#28984) - The default value of the `-mempoolfullrbf` configuration option has been changed from 0 to 1, i.e. `mempoolfullrbf=1`. (#30493) Updated RPCs ------------ - The `dumptxoutset` RPC now returns the UTXO set dump in a new and improved format. Correspondingly, the `loadtxoutset` RPC now expects this new format in the dumps it tries to load. Dumps with the old format are no longer supported and need to be recreated using the new format to be usable. (#29612) - AssumeUTXO mainnet parameters have been added for height 840,000. This means the `loadtxoutset` RPC can now be used on mainnet with the matching UTXO set from that height. (#28553) - The `warnings` field in `getblockchaininfo`, `getmininginfo` and `getnetworkinfo` now returns all the active node warnings as an array of strings, instead of a single warning. The current behaviour can be temporarily restored by running Bitcoin Core with the configuration option `-deprecatedrpc=warnings`. (#29845) - Previously when using the `sendrawtransaction` RPC and specifying outputs that are already in the UTXO set, an RPC error code of `-27` with the message "Transaction already in block chain" was returned in response. The error message has been changed to "Transaction outputs already in utxo set" to more accurately describe the source of the issue. (#30212) - The default mode for the `estimatesmartfee` RPC has been updated from `conservative` to `economical`, which is expected to reduce over-estimation for many users, particularly if Replace-by-Fee is an option. For users that require high confidence in their fee estimates at the cost of potentially over-estimating, the `conservative` mode remains available. (#30275) - RPC `scantxoutset` now returns 2 new fields in the "unspents" JSON array: `blockhash` and `confirmations`. See the scantxoutset help for details. (#30515) - RPC `submitpackage` now allows 2 new arguments to be passed: `maxfeerate` and `maxburnamount`. See the subtmitpackage help for details. (#28950) Changes to wallet-related RPCs can be found in the Wallet section below. Updated REST APIs ----------------- - Parameter validation for `/rest/getutxos` has been improved by rejecting truncated or overly large txids and malformed outpoint indices via raising an HTTP_BAD_REQUEST "Parse error". These requests were previously handled silently. (#30482, #30444) Build System ------------ - GCC 11.1 or later, or Clang 16.0 or later, are now required to compile Bitcoin Core. (#29091, #30263) - The minimum required glibc to run Bitcoin Core is now 2.31. This means that RHEL 8 and Ubuntu 18.04 (Bionic) are no-longer supported. (#29987) - `--enable-lcov-branch-coverage` has been removed, given incompatibilities between lcov version 1 & 2. `LCOV_OPTS` should be used to set any options instead. (#30192) Updated Settings ---------------- - When running with `-alertnotify`, an alert can now be raised multiple times instead of just once. Previously, it was only raised when unknown new consensus rules were activated. Its scope has now been increased to include all kernel warnings. Specifically, alerts will now also be raised when an invalid chain with a large amount of work has been detected. Additional warnings may be added in the future. (#30058) Changes to GUI or wallet related settings can be found in the GUI or Wallet section below. Wallet ------ - The wallet now detects when wallet transactions conflict with the mempool. Mempool-conflicting transactions can be seen in the `"mempoolconflicts"` field of `gettransaction`. The inputs of mempool-conflicted transactions can now be respent without manually abandoning the transactions when the parent transaction is dropped from the mempool, which can cause wallet balances to appear higher. (#27307) - A new `max_tx_weight` option has been added to the RPCs `fundrawtransaction`, `walletcreatefundedpsbt`, and `send`. It specifies the maximum transaction weight. If the limit is exceeded during funding, the transaction will not be built. The default value is 4,000,000 WU. (#29523) - A new `createwalletdescriptor` RPC allows users to add new automatically generated descriptors to their wallet. This can be used to upgrade wallets created prior to the introduction of a new standard descriptor, such as taproot. (#29130) - A new RPC `gethdkeys` lists all of the BIP32 HD keys in use by all of the descriptors in the wallet. These keys can be used in conjunction with `createwalletdescriptor` to create and add single key descriptors to the wallet for a particular key that the wallet already knows. (#29130) - The `sendall` RPC can now spend unconfirmed change and will include additional fees as necessary for the resulting transaction to bump the unconfirmed transactions' feerates to the specified feerate. (#28979) - In RPC `bumpfee`, if a `fee_rate` is specified, the feerate is no longer restricted to following the wallet's incremental feerate of 5 sat/vb. The feerate must still be at least the sum of the original fee and the mempool's incremental feerate. (#27969) GUI Changes ----------- - The "Migrate Wallet" menu allows users to migrate any legacy wallet in their wallet directory, regardless of the wallets loaded. (gui#824) - The "Information" window now displays the maximum mempool size along with the mempool usage. (gui#825) Low-level Changes ================= Tests ----- - The BIP94 timewarp attack mitigation is now active on the `regtest` network. (#30681) - A new `-testdatadir` option has been added to `test_bitcoin` to allow specifying the location of unit test data directories. (#26564) Blockstorage ------------ - Block files are now XOR'd by default with a key stored in the blocksdir. Previous releases of Bitcoin Core or previous external software will not be able to read the blocksdir with a non-zero XOR-key. Refer to the `-blocksxor` help for more details. (#28052) Chainstate ---------- - The chainstate database flushes that occur when blocks are pruned will no longer empty the database cache. The cache will remain populated longer, which significantly reduces the time for initial block download to complete. (#28280) Dependencies ------------ - The dependency on Boost.Process has been replaced with cpp-subprocess, which is contained in source. Builders will no longer need Boost.Process to build with external signer support. (#28981) Credits ======= Thanks to everyone who directly contributed to this release: - 0xb10c - Alfonso Roman Zubeldia - Andrew Toth - AngusP - Anthony Towns - Antoine Poinsot - Anton A - Ava Chow - Ayush Singh - Ben Westgate - Brandon Odiwuor - brunoerg - bstin - Charlie - Christopher Bergqvist - Cory Fields - crazeteam - Daniela Brozzoni - David Gumberg - dergoegge - Edil Medeiros - Epic Curious - Fabian Jahr - fanquake - furszy - glozow - Greg Sanders - hanmz - Hennadii Stepanov - Hernan Marino - Hodlinator - ishaanam - ismaelsadeeq - Jadi - Jon Atack - josibake - jrakibi - kevkevin - kevkevinpal - Konstantin Akimov - laanwj - Larry Ruane - Lőrinc - Luis Schwab - Luke Dashjr - MarcoFalke - marcofleon - Marnix - Martin Saposnic - Martin Zumsande - Matt Corallo - Matthew Zipkin - Matt Whitlock - Max Edwards - Michael Dietz - Murch - nanlour - pablomartin4btc - Peter Todd - Pieter Wuille - @RandyMcMillan - RoboSchmied - Roman Zeyde - Ryan Ofsky - Sebastian Falbesoner - Sergi Delgado Segura - Sjors Provoost - spicyzboss - StevenMia - stickies-v - stratospher - Suhas Daftuar - sunerok - tdb3 - TheCharlatan - umiumi - Vasil Dimov - virtu - willcl-ark As well as to everyone that helped with translations on [Transifex](https://www.transifex.com/bitcoin/bitcoin/). @ 592295cf:413a0db9
2024-10-05 09:32:22# Week 30th September Wiki article on the topic. [sPhil] (https://sphil.xyz/) Religion politics philosophy history are critical. They are not objective things. Week of updates for protocol apps, including Gossip, coracle app, nostrmo, nostur and many others. ------- Kind7 Tags: K, emoji,a,others Others threads multi people -------- Show likes as kind 1 This person liked this post. Or this post has three likes in your timeline. The likes I don't know in your timeline really interest you. 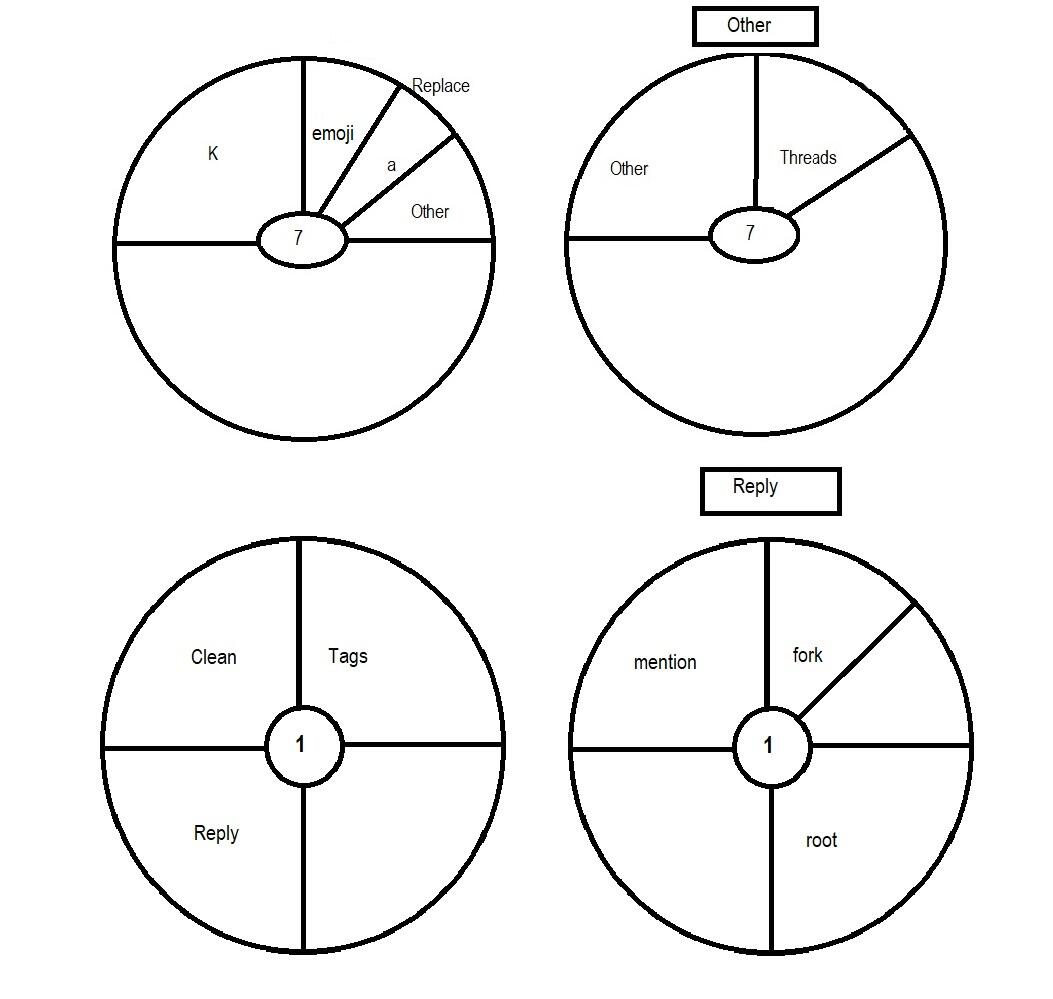 ---------- The first book is the bible... Word of Alexandria. I added cyberspace to the difficult things of the protocol ultra brain things. Low brain, middle brain, top brain, ultra. Some alphaama codes .AA u login .AA q stuff .AA q run b .AA q run f .AA q close f high things of alphaama nostr:nevent1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqlqu2vwpwax7dj420e75yws7g7vyua9e245c0x73c056gunxchluey4q99 ------------------- Comment: nostr:nevent1qqs8pn0zzhgk5l2raqh736rj3ckm48pfl6r7m72rnz2r2p7lzgmx20gzyqduwzspfzelx9k6x0lrez0j8cl8rtz0lxvqylk8z2ustnfy76jpzqcyqqqqqqgpramhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjsjt5rvu ----------- You have to get to the point where you have your community relay. But you have to go down the rabbit hole of relays. General, search, local, inbox outbox, cache. Etc until you get to community relay that is being talked about these days because of NIP 29 "Relay-based Groups". In the end you have to have that table with the various types of relays clearly in your mind. If the user doesn't think about it, who should think about it, who? if I choose the relays? ----------- NIP-100 the world to make community for me. NIP-28 + NIP-72. So you have some structure interoperability with kind1. But the Channel is another kind. You arrange the various channels in the community. No posts need to be approved. It's useless Protocol users are becoming more reddit users or so. I don't want to deal with these people.
@ 592295cf:413a0db9
2024-10-05 09:32:22# Week 30th September Wiki article on the topic. [sPhil] (https://sphil.xyz/) Religion politics philosophy history are critical. They are not objective things. Week of updates for protocol apps, including Gossip, coracle app, nostrmo, nostur and many others. ------- Kind7 Tags: K, emoji,a,others Others threads multi people -------- Show likes as kind 1 This person liked this post. Or this post has three likes in your timeline. The likes I don't know in your timeline really interest you. 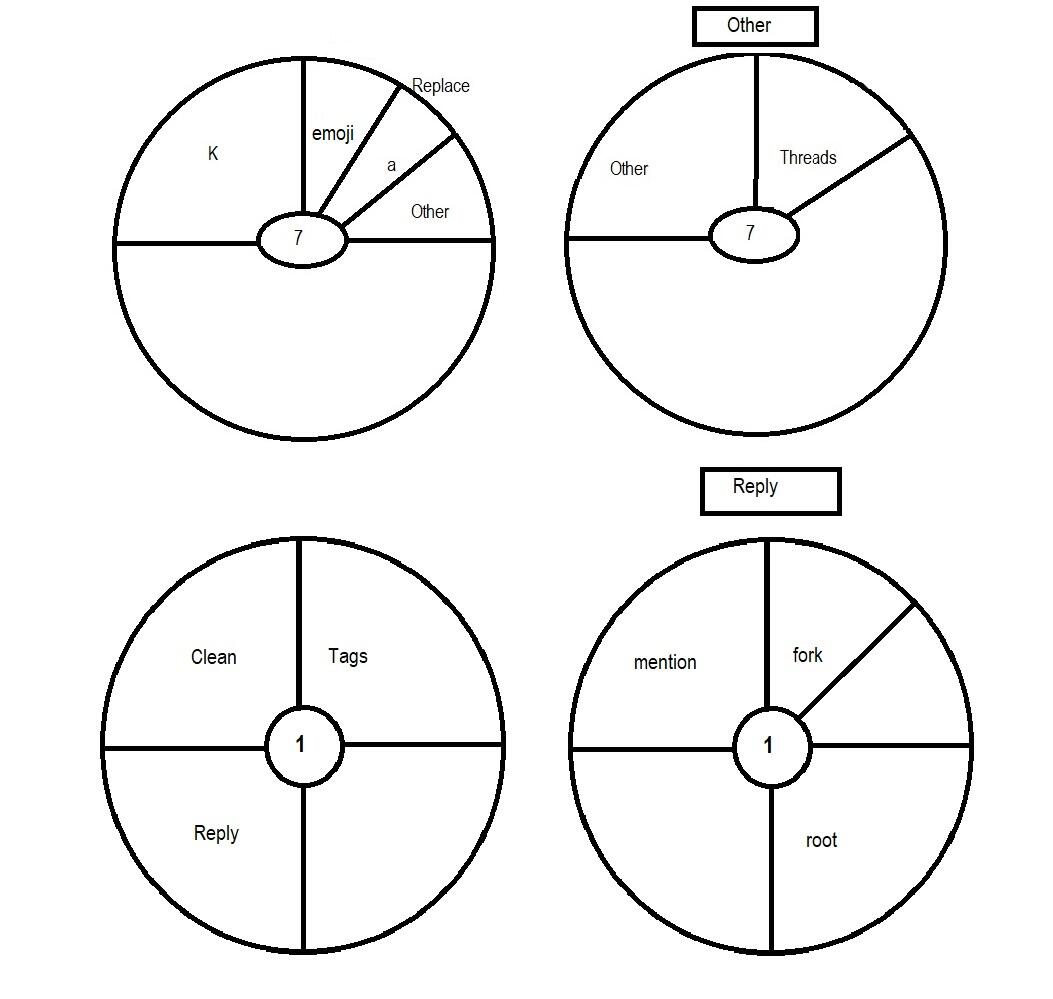 ---------- The first book is the bible... Word of Alexandria. I added cyberspace to the difficult things of the protocol ultra brain things. Low brain, middle brain, top brain, ultra. Some alphaama codes .AA u login .AA q stuff .AA q run b .AA q run f .AA q close f high things of alphaama nostr:nevent1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqlqu2vwpwax7dj420e75yws7g7vyua9e245c0x73c056gunxchluey4q99 ------------------- Comment: nostr:nevent1qqs8pn0zzhgk5l2raqh736rj3ckm48pfl6r7m72rnz2r2p7lzgmx20gzyqduwzspfzelx9k6x0lrez0j8cl8rtz0lxvqylk8z2ustnfy76jpzqcyqqqqqqgpramhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjsjt5rvu ----------- You have to get to the point where you have your community relay. But you have to go down the rabbit hole of relays. General, search, local, inbox outbox, cache. Etc until you get to community relay that is being talked about these days because of NIP 29 "Relay-based Groups". In the end you have to have that table with the various types of relays clearly in your mind. If the user doesn't think about it, who should think about it, who? if I choose the relays? ----------- NIP-100 the world to make community for me. NIP-28 + NIP-72. So you have some structure interoperability with kind1. But the Channel is another kind. You arrange the various channels in the community. No posts need to be approved. It's useless Protocol users are becoming more reddit users or so. I don't want to deal with these people. @ ec9bd746:df11a9d0
2024-10-04 09:46:21It's intriguing to me how beer prices have changed since 1999. Today, you can buy Braník on sale for 9.90 Kč, so for 100 Kč you get 10 beers. 25 years ago, you'd get 13.5 beers for the same amount. What does that tell us? - **The cost of labor and services has gone up a lot**, but people are willing to pay and even expect a certain level of quality. There are way fewer run-down pubs than before. - **Production has become much more efficient**, so considering inflation and purchasing power, bottled beer is actually cheaper now than it used to be. In 1995, about 30 years ago, bottled and draft beer cost almost the same—around 7 Kč. ([Source in Czech](https://hn.cz/c1-60157680-jak-se-menily-ceny-co-jste-si-mohli-dovolit-v-roce-1995-a-co-dnes)) **So what's the takeaway?** 1. **A wealthy society can afford much pricier services.** 2. **Prices of basic groceries and fast-moving goods are squeezed to the bone.** The best way to gauge real inflation is at the supermarket, where there's no room for messing with margins, stock levels, seasonality, etc. Everything moves fast, competition is huge, and big retailers are relentless. Real estate is pricey due to artificial (or bureaucracy-induced) shortages, but meat, milk, beer, bread, etc., are operating on razor-thin profits. That's why they react so quickly—see point 2.
@ ec9bd746:df11a9d0
2024-10-04 09:46:21It's intriguing to me how beer prices have changed since 1999. Today, you can buy Braník on sale for 9.90 Kč, so for 100 Kč you get 10 beers. 25 years ago, you'd get 13.5 beers for the same amount. What does that tell us? - **The cost of labor and services has gone up a lot**, but people are willing to pay and even expect a certain level of quality. There are way fewer run-down pubs than before. - **Production has become much more efficient**, so considering inflation and purchasing power, bottled beer is actually cheaper now than it used to be. In 1995, about 30 years ago, bottled and draft beer cost almost the same—around 7 Kč. ([Source in Czech](https://hn.cz/c1-60157680-jak-se-menily-ceny-co-jste-si-mohli-dovolit-v-roce-1995-a-co-dnes)) **So what's the takeaway?** 1. **A wealthy society can afford much pricier services.** 2. **Prices of basic groceries and fast-moving goods are squeezed to the bone.** The best way to gauge real inflation is at the supermarket, where there's no room for messing with margins, stock levels, seasonality, etc. Everything moves fast, competition is huge, and big retailers are relentless. Real estate is pricey due to artificial (or bureaucracy-induced) shortages, but meat, milk, beer, bread, etc., are operating on razor-thin profits. That's why they react so quickly—see point 2. @ e6817453:b0ac3c39
2024-09-30 14:52:23In the modern world of AI, managing vast amounts of data while keeping it relevant and accessible is a significant challenge, mainly when dealing with large language models (LLMs) and vector databases. One approach that has gained prominence in recent years is integrating vector search with metadata, especially in retrieval-augmented generation (RAG) pipelines. Vector search and metadata enable faster and more accurate data retrieval. However, the process of pre- and post-search filtering results plays a crucial role in ensuring data relevance. <iframe width="560" height="315" src="https://www.youtube.com/embed/BkNqu51et9U?si=lne0jWxdrZPxSgd1" title="YouTube video player" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen></iframe> ## The Vector Search and Metadata Challenge In a typical vector search, you create embeddings from chunks of text, such as a PDF document. These embeddings allow the system to search for similar items and retrieve them based on relevance. The challenge, however, arises when you need to combine vector search results with structured metadata. For example, you may have timestamped text-based content and want to retrieve the most relevant content within a specific date range. This is where metadata becomes critical in refining search results. Unfortunately, most vector databases treat metadata as a secondary feature, isolating it from the primary vector search process. As a result, handling queries that combine vectors and metadata can become a challenge, particularly when the search needs to account for a dynamic range of filters, such as dates or other structured data. ## LibSQL and vector search metadata LibSQL is a more general-purpose SQLite-based database that adds vector capabilities to regular data. Vectors are presented as blob columns of regular tables. It makes vector embeddings and metadata a first-class citizen that naturally builds deep integration of these data points. ``` create table if not exists conversation ( id varchar(36) primary key not null, startDate real, endDate real, summary text, vectorSummary F32_BLOB(512) ); ``` It solves the challenge of metadata and vector search and eliminates impedance between vector data and regular structured data points in the same storage. As you can see, you can access vector-like data and start date in the same query. ``` select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from conversation where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top}; ``` **vector\_distance\_cos** calculated as distance allows us to make a primitive vector search that does a full scan and calculates distances on rows. We could optimize it with CTE and limit search and distance calculations to a much smaller subset of data. This approach could be calculation intensive and fail on large amounts of data. Libsql offers a way more effective vector search based on FlashDiskANN vector indexed. ``` vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i ``` **vector\_top\_k** is a table function that searches for the top of the newly created vector search index. As you can see, we could use only vector as a function parameter, and other columns could be used outside of the table function. So, to use a vector index together with different columns, we need to apply some strategies. Now we get a classical problem of integration vector search results with metadata queries. ## Post-Filtering: A Common Approach The most widely adopted method in these pipelines is **post-filtering**. In this approach, the system first retrieves data based on vector similarities and then applies metadata filters. For example, imagine you’re conducting a vector search to retrieve conversations relevant to a specific question. Still, you also want to ensure these conversations occurred in the past week. 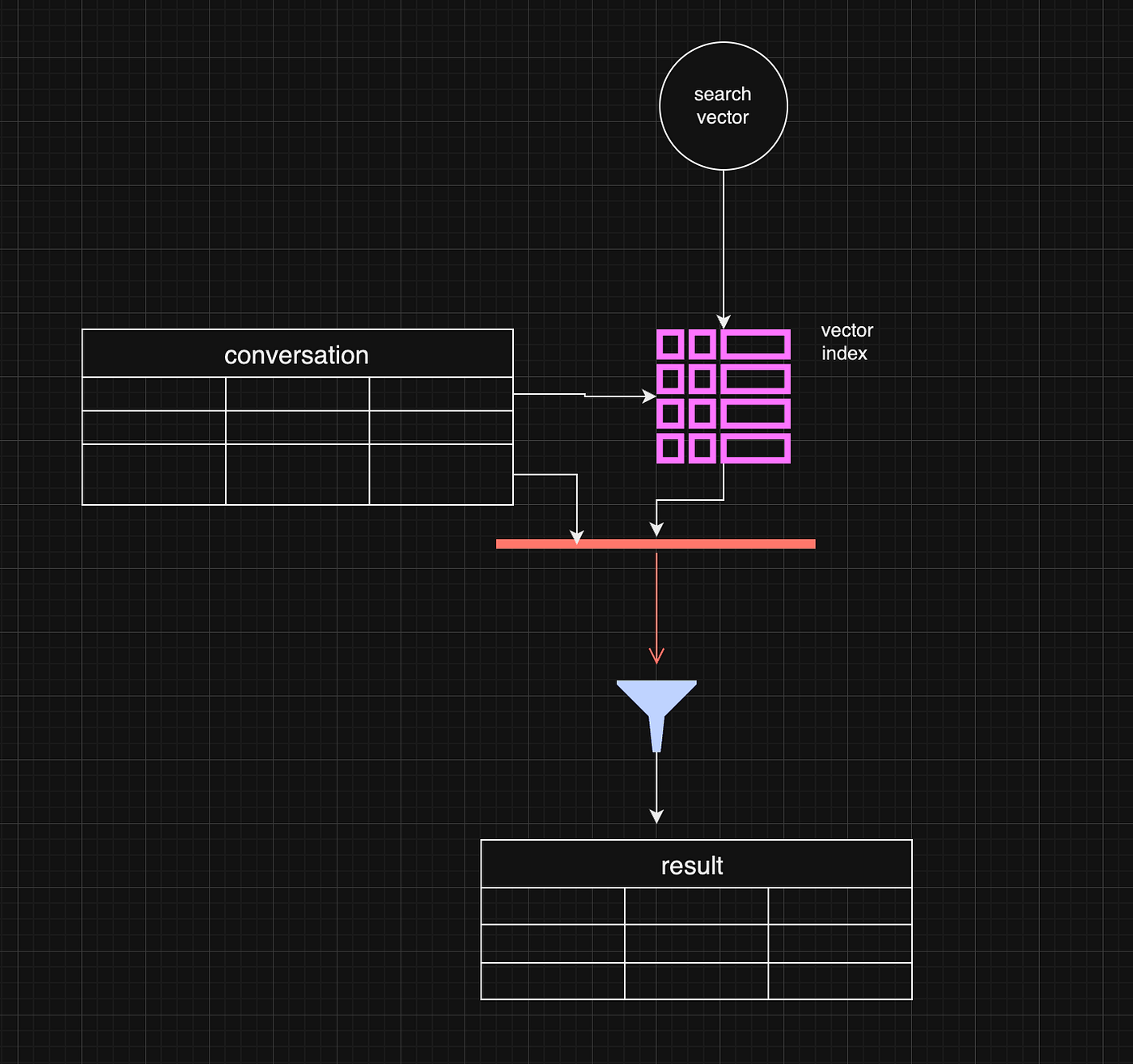 Post-filtering allows the system to retrieve the most relevant vector-based results and subsequently filter out any that don’t meet the metadata criteria, such as date range. This method is efficient when vector similarity is the primary factor driving the search, and metadata is only applied as a secondary filter. ``` const sqlQuery = ` select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i inner join conversation c on i.id = c.rowid where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top}; ``` However, there are some limitations. For example, the initial vector search may yield fewer results or omit some relevant data before applying the metadata filter. If the search window is narrow enough, this can lead to complete results. One working strategy is to make the top value in vector\_top\_K much bigger. Be careful, though, as the function's default max number of results is around 200 rows. ## Pre-Filtering: A More Complex Approach Pre-filtering is a more intricate approach but can be more effective in some instances. In pre-filtering, metadata is used as the primary filter before vector search takes place. This means that only data that meets the metadata criteria is passed into the vector search process, limiting the scope of the search right from the beginning. While this approach can significantly reduce the amount of irrelevant data in the final results, it comes with its own challenges. For example, pre-filtering requires a deeper understanding of the data structure and may necessitate denormalizing the data or creating separate pre-filtered tables. This can be resource-intensive and, in some cases, impractical for dynamic metadata like date ranges. 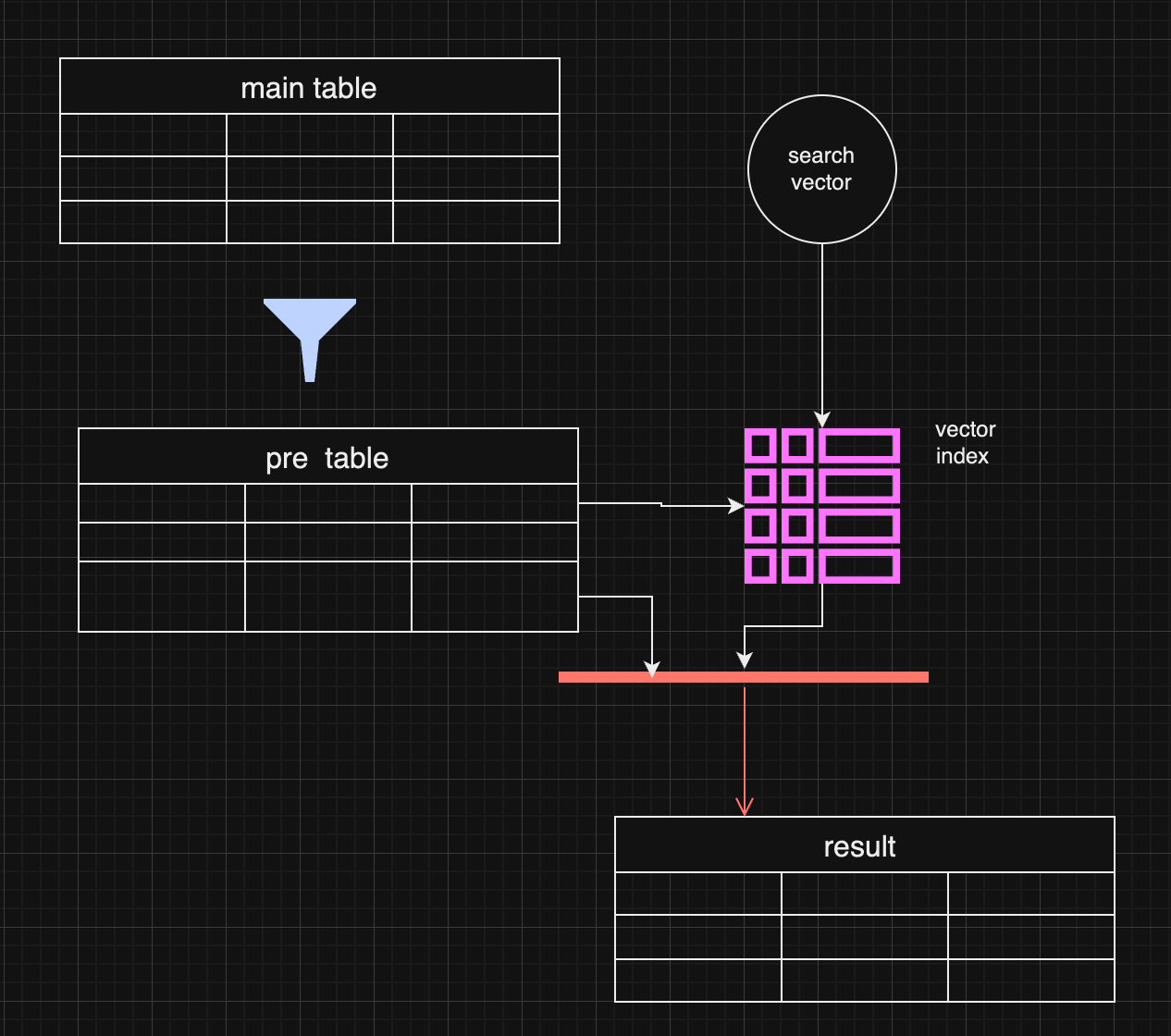 In certain use cases, pre-filtering might outperform post-filtering. For instance, when the metadata (e.g., specific date ranges) is the most important filter, pre-filtering ensures the search is conducted only on the most relevant data. ## Pre-filtering with distance-based filtering So, we are getting back to an old concept. We do prefiltering instead of using a vector index. ``` WITH FilteredDates AS ( SELECT c.id, c.startDate, c.endDate, c.summary, c.vectorSummary FROM YourTable c WHERE ${startDate ? `AND c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `AND c.endDate <= ${endDate.getTime()}` : ''} ), DistanceCalculation AS ( SELECT fd.id, fd.startDate, fd.endDate, fd.summary, fd.vectorSummary, vector_distance_cos(fd.vectorSummary, vector(${vector})) AS distance FROM FilteredDates fd ) SELECT dc.id, dc.startDate, dc.endDate, dc.summary, dc.distance FROM DistanceCalculation dc WHERE 1=1 ${distance ? `AND dc.distance <= ${distance}` : ''} ORDER BY dc.distance LIMIT ${top}; ``` It makes sense if the filter produces small data and distance calculation happens on the smaller data set. 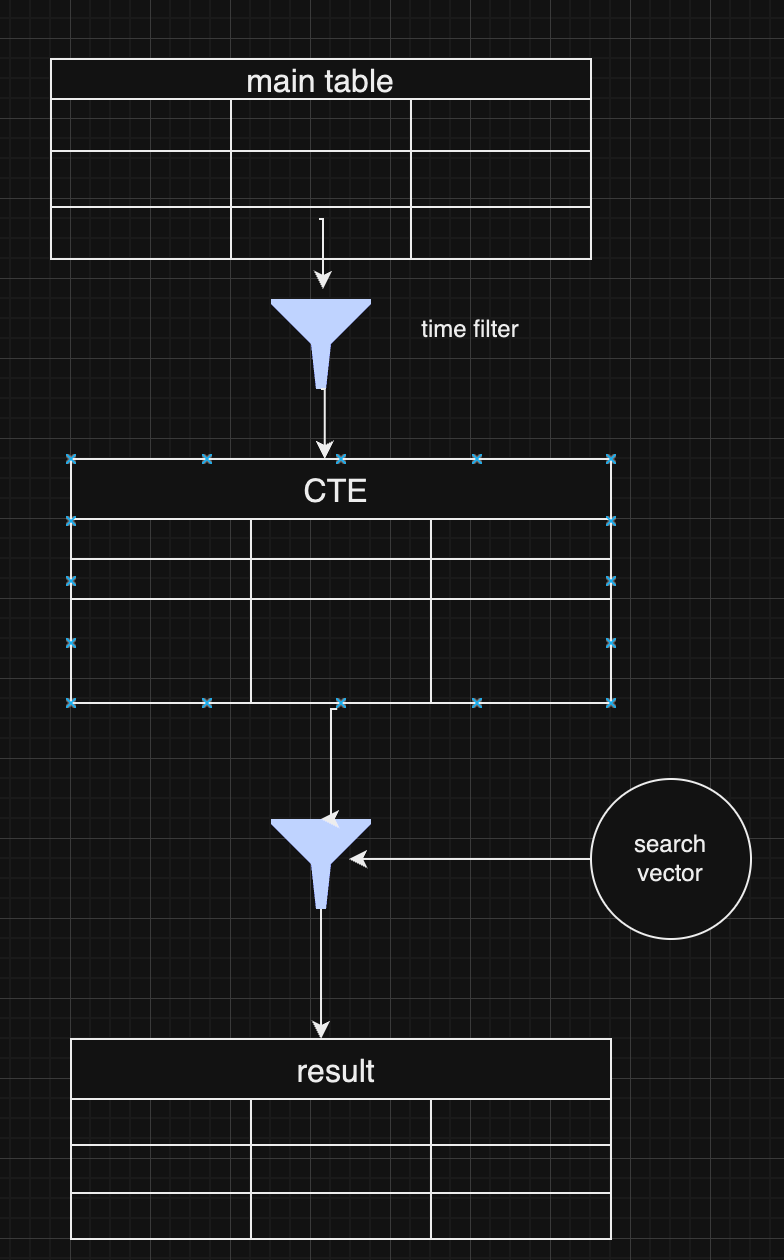 As a pro of this approach, you have full control over the data and get all results without omitting some typical values for extensive index searches. ## Choosing Between Pre and Post-Filtering Both pre-filtering and post-filtering have their advantages and disadvantages. Post-filtering is more accessible to implement, especially when vector similarity is the primary search factor, but it can lead to incomplete results. Pre-filtering, on the other hand, can yield more accurate results but requires more complex data handling and optimization. In practice, many systems combine both strategies, depending on the query. For example, they might start with a broad pre-filtering based on metadata (like date ranges) and then apply a more targeted vector search with post-filtering to refine the results further. ## **Conclusion** Vector search with metadata filtering offers a powerful approach for handling large-scale data retrieval in LLMs and RAG pipelines. Whether you choose pre-filtering or post-filtering—or a combination of both—depends on your application's specific requirements. As vector databases continue to evolve, future innovations that combine these two approaches more seamlessly will help improve data relevance and retrieval efficiency further.
@ e6817453:b0ac3c39
2024-09-30 14:52:23In the modern world of AI, managing vast amounts of data while keeping it relevant and accessible is a significant challenge, mainly when dealing with large language models (LLMs) and vector databases. One approach that has gained prominence in recent years is integrating vector search with metadata, especially in retrieval-augmented generation (RAG) pipelines. Vector search and metadata enable faster and more accurate data retrieval. However, the process of pre- and post-search filtering results plays a crucial role in ensuring data relevance. <iframe width="560" height="315" src="https://www.youtube.com/embed/BkNqu51et9U?si=lne0jWxdrZPxSgd1" title="YouTube video player" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen></iframe> ## The Vector Search and Metadata Challenge In a typical vector search, you create embeddings from chunks of text, such as a PDF document. These embeddings allow the system to search for similar items and retrieve them based on relevance. The challenge, however, arises when you need to combine vector search results with structured metadata. For example, you may have timestamped text-based content and want to retrieve the most relevant content within a specific date range. This is where metadata becomes critical in refining search results. Unfortunately, most vector databases treat metadata as a secondary feature, isolating it from the primary vector search process. As a result, handling queries that combine vectors and metadata can become a challenge, particularly when the search needs to account for a dynamic range of filters, such as dates or other structured data. ## LibSQL and vector search metadata LibSQL is a more general-purpose SQLite-based database that adds vector capabilities to regular data. Vectors are presented as blob columns of regular tables. It makes vector embeddings and metadata a first-class citizen that naturally builds deep integration of these data points. ``` create table if not exists conversation ( id varchar(36) primary key not null, startDate real, endDate real, summary text, vectorSummary F32_BLOB(512) ); ``` It solves the challenge of metadata and vector search and eliminates impedance between vector data and regular structured data points in the same storage. As you can see, you can access vector-like data and start date in the same query. ``` select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from conversation where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top}; ``` **vector\_distance\_cos** calculated as distance allows us to make a primitive vector search that does a full scan and calculates distances on rows. We could optimize it with CTE and limit search and distance calculations to a much smaller subset of data. This approach could be calculation intensive and fail on large amounts of data. Libsql offers a way more effective vector search based on FlashDiskANN vector indexed. ``` vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i ``` **vector\_top\_k** is a table function that searches for the top of the newly created vector search index. As you can see, we could use only vector as a function parameter, and other columns could be used outside of the table function. So, to use a vector index together with different columns, we need to apply some strategies. Now we get a classical problem of integration vector search results with metadata queries. ## Post-Filtering: A Common Approach The most widely adopted method in these pipelines is **post-filtering**. In this approach, the system first retrieves data based on vector similarities and then applies metadata filters. For example, imagine you’re conducting a vector search to retrieve conversations relevant to a specific question. Still, you also want to ensure these conversations occurred in the past week. 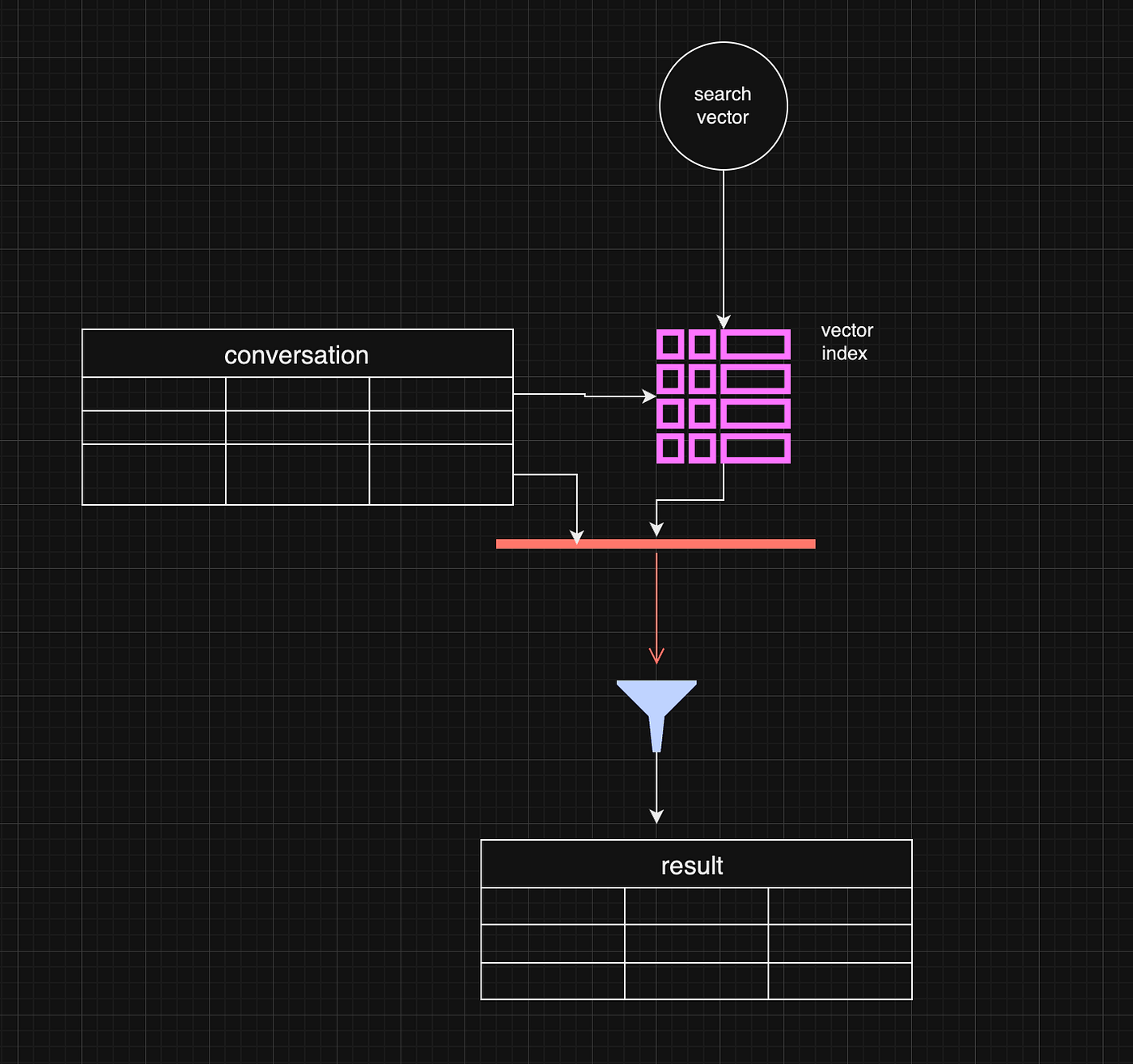 Post-filtering allows the system to retrieve the most relevant vector-based results and subsequently filter out any that don’t meet the metadata criteria, such as date range. This method is efficient when vector similarity is the primary factor driving the search, and metadata is only applied as a secondary filter. ``` const sqlQuery = ` select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i inner join conversation c on i.id = c.rowid where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top}; ``` However, there are some limitations. For example, the initial vector search may yield fewer results or omit some relevant data before applying the metadata filter. If the search window is narrow enough, this can lead to complete results. One working strategy is to make the top value in vector\_top\_K much bigger. Be careful, though, as the function's default max number of results is around 200 rows. ## Pre-Filtering: A More Complex Approach Pre-filtering is a more intricate approach but can be more effective in some instances. In pre-filtering, metadata is used as the primary filter before vector search takes place. This means that only data that meets the metadata criteria is passed into the vector search process, limiting the scope of the search right from the beginning. While this approach can significantly reduce the amount of irrelevant data in the final results, it comes with its own challenges. For example, pre-filtering requires a deeper understanding of the data structure and may necessitate denormalizing the data or creating separate pre-filtered tables. This can be resource-intensive and, in some cases, impractical for dynamic metadata like date ranges. 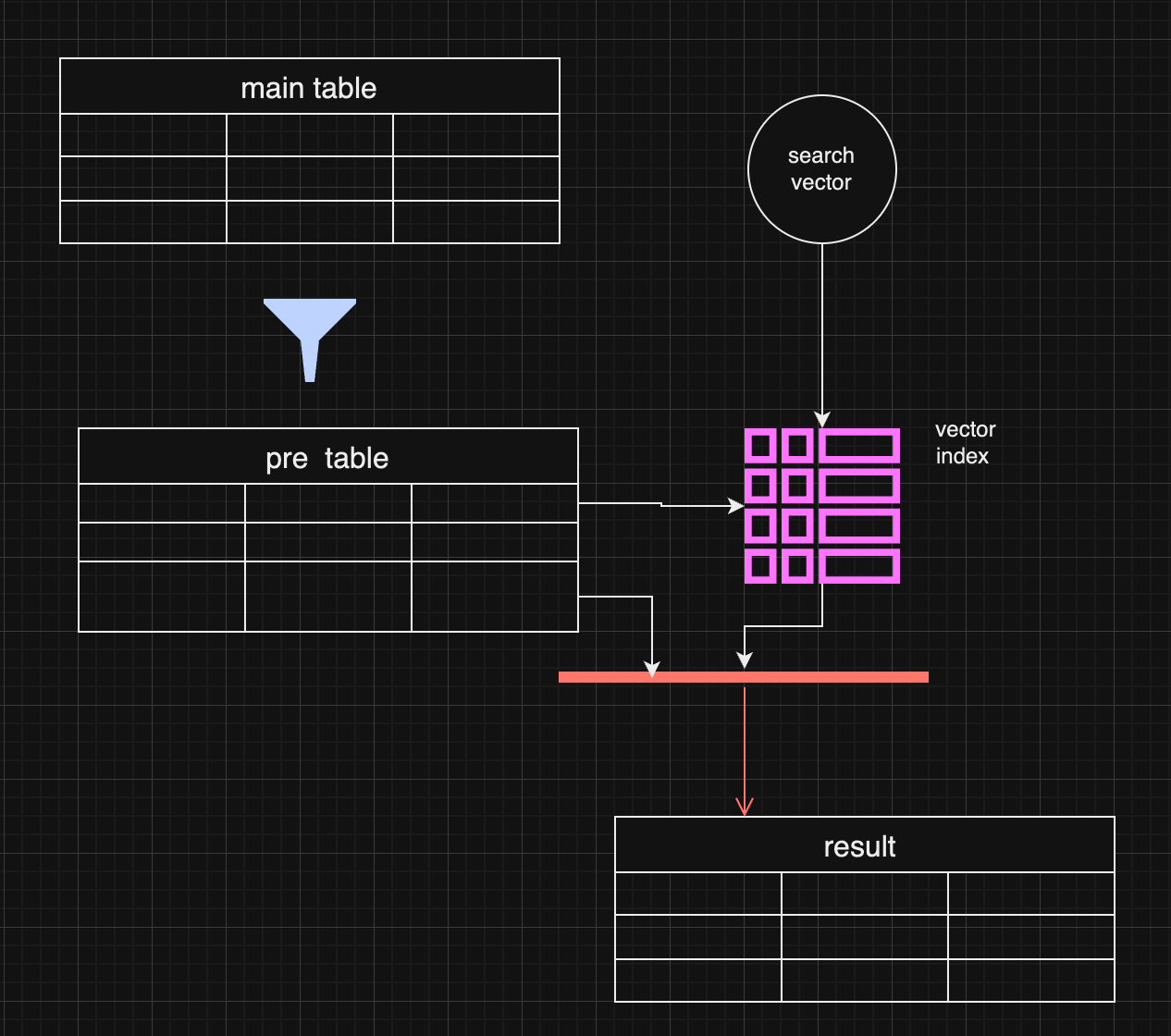 In certain use cases, pre-filtering might outperform post-filtering. For instance, when the metadata (e.g., specific date ranges) is the most important filter, pre-filtering ensures the search is conducted only on the most relevant data. ## Pre-filtering with distance-based filtering So, we are getting back to an old concept. We do prefiltering instead of using a vector index. ``` WITH FilteredDates AS ( SELECT c.id, c.startDate, c.endDate, c.summary, c.vectorSummary FROM YourTable c WHERE ${startDate ? `AND c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `AND c.endDate <= ${endDate.getTime()}` : ''} ), DistanceCalculation AS ( SELECT fd.id, fd.startDate, fd.endDate, fd.summary, fd.vectorSummary, vector_distance_cos(fd.vectorSummary, vector(${vector})) AS distance FROM FilteredDates fd ) SELECT dc.id, dc.startDate, dc.endDate, dc.summary, dc.distance FROM DistanceCalculation dc WHERE 1=1 ${distance ? `AND dc.distance <= ${distance}` : ''} ORDER BY dc.distance LIMIT ${top}; ``` It makes sense if the filter produces small data and distance calculation happens on the smaller data set. 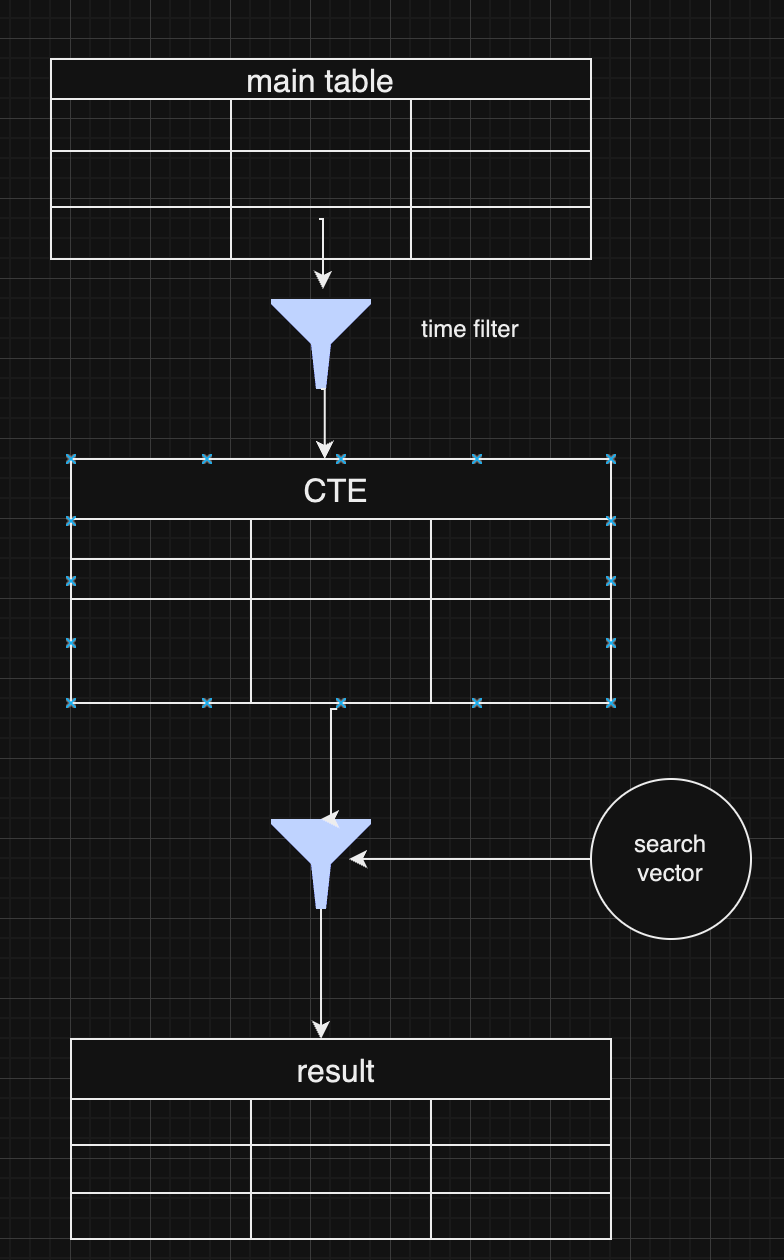 As a pro of this approach, you have full control over the data and get all results without omitting some typical values for extensive index searches. ## Choosing Between Pre and Post-Filtering Both pre-filtering and post-filtering have their advantages and disadvantages. Post-filtering is more accessible to implement, especially when vector similarity is the primary search factor, but it can lead to incomplete results. Pre-filtering, on the other hand, can yield more accurate results but requires more complex data handling and optimization. In practice, many systems combine both strategies, depending on the query. For example, they might start with a broad pre-filtering based on metadata (like date ranges) and then apply a more targeted vector search with post-filtering to refine the results further. ## **Conclusion** Vector search with metadata filtering offers a powerful approach for handling large-scale data retrieval in LLMs and RAG pipelines. Whether you choose pre-filtering or post-filtering—or a combination of both—depends on your application's specific requirements. As vector databases continue to evolve, future innovations that combine these two approaches more seamlessly will help improve data relevance and retrieval efficiency further. @ 472f440f:5669301e
2024-09-25 04:12:35Last night I had the pleasure of sitting down with Caitlin Long, Founder and CEO of Custodia - a fully reserved bank providing banking services to bitcoin companies, to discuss an affidavit written by Elaine Hetrick of Silvergate Bank. Elaine is the Chief Administrative Officer of Silvergate and wrote an affidavit, a sworn testimony subject to perjury, in which she detailed the events that led to Silvergate voluntarily winding down their business and returning deposits to their customers. This affidavit is a bombshell because it confirms speculation that Silvergate was solvent in early 2023 and wasn't shut down because of bad risk management on behalf of the bank's management team, but instead was forced to shutter its doors because the Biden Administration, with strong influence from Senator Elizabeth Warren, forced Silvergate's hand because they didn't like that they were banking digital asset companies. For those who are a bit fuzzy on the details of the narratives that were flying around Silvergate at the time, I'll jog your memory. FTX was a customer of Silvergate's at the time their Ponzi scheme unraveled. As FTX was blowing up, everyone and their mother was scrambling to get their money out of Silvergate because they assumed that since one of the bank's largest counterparties was going bust, the bank must be in trouble too. A sane decision. Especially considering the history of systemically non-important financial institutions this century. Unless you were paying close attention during this time, you were likely under the impression that Silvergate was a typical fractionally reserved bank that was experiencing a run that led to its inevitable demise. The media made it seem this way. The regulators made it seem this way. And one pompous short seller made it seem this way. However, nothing could be further from the truth. Here are the most important parts of the affidavit: > Silvergate had stabilized, was able to make regulatory capital requirements, and had the capability to continue to serve its customers that had kept their deposits with Silvergate Bank. Despite this, regulators decided to turn the pressure up and essentially gave Silvergate Bank, and Signature Bank as well, an ultimatum; drastically change your business models immediately by dropping your digital asset customer base or we'll shut you down. There were no hard numbers described in Elaine's testimony, but rumors are that the regulators wanted Silvergate to quickly shrink their exposure to digital asset-related clients to less than 15% of their capital base. At the time, Silvergate's customer base was made up almost entirely of digital asset companies (99.5% to be exact). The regulators were asking Silvergate to do something that was quite literally impossible given the circumstances. Faced with an impossible task, on March 8th of 2023 Silvergate decided to voluntarily wind down their operations and return deposits back to their customers. Let's be very clear here, Silvergate did not lose a single penny of customer deposits due to the run on their bank. Management, understanding the volatile nature of the digital asset markets, designed their risk management and capital allocation strategies in a way that would enable them to return dollars to any customer who requested them. And that's exactly what they did when customers came to request their money. They returned EVERY SINGLE PENNY. This begs the question, "Why did they essentially force Silvergate to shut down?" They seemed to be running a very responsible operation after all. You'd think the regulators would applaud Silvergate's vigilance in risk management on behalf of their customer base. How many banks would have been able to do the same thing if put in the same situation? Probably not many. The answer to this question is already well known throughout the industry, but Elaine Hetrick's testimony adds some hard evidence that makes it undeniable; Elizabeth Warren, the SEC, the FDIC and the Federal Reserve have been acting in concert to unconstitutionally and extrajudicially target the bitcoin and broader digital asset industry because they do not believe that it should exist. It is a threat to their power structure. The financial system, as it is designed today, gives those who would like to centrally plan the economy and micromanage the lives of American citizens a ton of power. Bitcoin is a threat to that power and they have to do everything in their power to prevent its proliferation. The targeting of the industry was also confirmed by the aftermath of the NYDFS and FDIC uncharacteristically taking Signature Bank behind the woodshed in the evening of Sunday, March 20th, 2023, despite the fact that Barney Frank and others at the bank were convinced they could handle withdraws come market open the next day. Signature Bank was ultimately sold to Flagstar Bank. However, they were forced to spin out their digital asset-related accounts before doing so. This public signaling and sudden regulatory shift made clear that, at least as of the first quarter of 2023, the Federal Bank Regulatory Agencies would not tolerate banks with significant concentrations of digital asset customers, ultimately preventing Silvergate Bank from continuing its digital asset focused business model. Pretty damning if you ask me. Also, very frustrating and most definitely illegal. Elizabeth Warren and her gaggle of hall monitors across alphabet soup agencies and the Federal Reserve have been on one massive, unconstitutional, power trip for the last four years. They've besmirched bitcoin and those of us working hard to ensure that the United States of America leads the way forward as bitcoin adoption continues at every turn. Good people striving to make the world a better place. No one is a better example of this than Alan Lane, the former CEO of Silvergate Bank. I consider Alan a friend and feel supremely confident when I say that he is one of the nicest and thoughtful people I have met in this industry. A man who followed his passion to bring legitimacy and much needed banking services to an industry that the incumbents refused to touch. And he did bring legitimacy. As I explained earlier, Alan and his team understood the volatile nature of the industry and built their firm in a way that took this volatility into account. Silvergate did not fail, they were forced to shut down by Elizabeth Warren and her acolytes at the regulatory agencies. What's worse, Warren's vendetta against bitcoin and the digital asset industry incited the largest banking crisis this country had seen since 2008. Silvergate and Signature being taken behind the woodshed put everyone on their toes and bank runs started across the country. This led to the failure of First Republic, Silicon Valley Bank and a couple of smaller banks, forced the Fed to step in with their emergency BTFP program, and burdened taxpayers with $40B in FDIC costs that needed to be absorbed as a result. If it weren't for the bailouts things would have gotten completely out of control. All because Elizabeth Warren wants to live in a world in which we are forced to use CBDCs and unable to opt-in to bitcoin. The euthanasia of Silvergate and Signature are only the tip of the iceberg when it comes to Chokepoint 2.0. Caitlin Long and Custodia have been in a years long battle with the Federal Reserve to receive a Fed master account so that they can properly serve their customers. For those who are unaware, Custodia is a full-reserve bank that exist to serve bitcoin and digital asset businesses as well as other adjacent businesses like fintechs, banks and funds. Custodia is a chartered bank and special purpose depository institution that has built custody services so that customers can hold bitcoin within their bank accounts alongside their dollar accounts. Like Silvergate and Signature, Custodia has been singled out and unlawfully denied a master account with the Fed because the Federal Reserve doesn't want a bank like Custodia to exist. Either because they worry about the ramifications of the introduction of a full-reserve bank into a system dominated by fractional-reserve banks or they simply do not want to see bitcoin succeed. If we're being honest, it's probably a combination of the two. Despite what we, or anyone else, thinks about the potential effect a bank like Custodia could have on the market if it's granted a master account, the Fed's actions are unconstitutional in this case as well. This was made pretty clear (but yet to be determined by a court) in an amicus brief written by Paul Clement on behalf of Custodia earlier this Summer. The Fed is actively undermining the dual-banking system that was set up in this country to enable competition between state chartered banks and the Federal Reserve system. In the case of Custodia, the Federal Reserve is exhibiting expansive discretionary power that it has never shown before. Custodia is a state chartered special purpose depository institution in the state of Wyoming. Historically, it would be trivial for this type of state chartered bank to get a master account with the Fed. But for whatever reason (we know the reason) the Fed has been denying Custodia their right to this account for a number of years. To the point where Custodia was forced to sue the Federal Reserve and take their case to the courts. What's interesting about the saga of Custodia and the Fed is that it has forced Custodia's legal team to dig in and highlight where the Fed is overextending its reach and acting arbitrarily. In the amicus brief that was published in July of this year, Paul Clement argues that the way Federal Reserve Bank presidents are chosen is unconstitutional when you take into consideration the fact the these Fed branch presidents are unilaterally undermining state banking laws by denying master accounts. If they are going to unilaterally undermine state banking laws they need to be appointed by the President or an official acting on behalf of the Executive Branch. Federal Reserve Bank presidents aren't appointed by the President of the United States or any official acting with the authority of the Executive Branch. Instead, they are appointed by their boards, which are controlled by the privately held commercial banks who own them. The Federal Reserve system is clearly acting unconstitutionally when they deny Custodia from being assigned a master account. The people in power within the federal government and the Federal Reserve system are actively targeting the bitcoin and digital asset industry, acting extrajudicially and making a mockery of the rule of law in the United States. They are completely out of control and it is important that everyone who cares about the future of bitcoin in the United States and the future of the United States more broadly (even if you don't like bitcoin) speaks out and fights against these totalitarians as vehemently as possible. What they are doing is wrong. It's unconstitutional. And it is putting the future of our country at risk. If the federal government, the regulators and the Federal Reserve do not get out of the way and let law abiding citizens build the businesses they want and associate with businesses they want, those businesses will go elsewhere and the United States will be set back generations as a result. It's time to put these people in their place and let it be known that freedom will reign supreme in the Land of the Free. Fight! --- Final thought... I promised Parker Lewis that I would do cross fit on Friday morning and I'm using today's final thought as an accountability tool.
@ 472f440f:5669301e
2024-09-25 04:12:35Last night I had the pleasure of sitting down with Caitlin Long, Founder and CEO of Custodia - a fully reserved bank providing banking services to bitcoin companies, to discuss an affidavit written by Elaine Hetrick of Silvergate Bank. Elaine is the Chief Administrative Officer of Silvergate and wrote an affidavit, a sworn testimony subject to perjury, in which she detailed the events that led to Silvergate voluntarily winding down their business and returning deposits to their customers. This affidavit is a bombshell because it confirms speculation that Silvergate was solvent in early 2023 and wasn't shut down because of bad risk management on behalf of the bank's management team, but instead was forced to shutter its doors because the Biden Administration, with strong influence from Senator Elizabeth Warren, forced Silvergate's hand because they didn't like that they were banking digital asset companies. For those who are a bit fuzzy on the details of the narratives that were flying around Silvergate at the time, I'll jog your memory. FTX was a customer of Silvergate's at the time their Ponzi scheme unraveled. As FTX was blowing up, everyone and their mother was scrambling to get their money out of Silvergate because they assumed that since one of the bank's largest counterparties was going bust, the bank must be in trouble too. A sane decision. Especially considering the history of systemically non-important financial institutions this century. Unless you were paying close attention during this time, you were likely under the impression that Silvergate was a typical fractionally reserved bank that was experiencing a run that led to its inevitable demise. The media made it seem this way. The regulators made it seem this way. And one pompous short seller made it seem this way. However, nothing could be further from the truth. Here are the most important parts of the affidavit: > Silvergate had stabilized, was able to make regulatory capital requirements, and had the capability to continue to serve its customers that had kept their deposits with Silvergate Bank. Despite this, regulators decided to turn the pressure up and essentially gave Silvergate Bank, and Signature Bank as well, an ultimatum; drastically change your business models immediately by dropping your digital asset customer base or we'll shut you down. There were no hard numbers described in Elaine's testimony, but rumors are that the regulators wanted Silvergate to quickly shrink their exposure to digital asset-related clients to less than 15% of their capital base. At the time, Silvergate's customer base was made up almost entirely of digital asset companies (99.5% to be exact). The regulators were asking Silvergate to do something that was quite literally impossible given the circumstances. Faced with an impossible task, on March 8th of 2023 Silvergate decided to voluntarily wind down their operations and return deposits back to their customers. Let's be very clear here, Silvergate did not lose a single penny of customer deposits due to the run on their bank. Management, understanding the volatile nature of the digital asset markets, designed their risk management and capital allocation strategies in a way that would enable them to return dollars to any customer who requested them. And that's exactly what they did when customers came to request their money. They returned EVERY SINGLE PENNY. This begs the question, "Why did they essentially force Silvergate to shut down?" They seemed to be running a very responsible operation after all. You'd think the regulators would applaud Silvergate's vigilance in risk management on behalf of their customer base. How many banks would have been able to do the same thing if put in the same situation? Probably not many. The answer to this question is already well known throughout the industry, but Elaine Hetrick's testimony adds some hard evidence that makes it undeniable; Elizabeth Warren, the SEC, the FDIC and the Federal Reserve have been acting in concert to unconstitutionally and extrajudicially target the bitcoin and broader digital asset industry because they do not believe that it should exist. It is a threat to their power structure. The financial system, as it is designed today, gives those who would like to centrally plan the economy and micromanage the lives of American citizens a ton of power. Bitcoin is a threat to that power and they have to do everything in their power to prevent its proliferation. The targeting of the industry was also confirmed by the aftermath of the NYDFS and FDIC uncharacteristically taking Signature Bank behind the woodshed in the evening of Sunday, March 20th, 2023, despite the fact that Barney Frank and others at the bank were convinced they could handle withdraws come market open the next day. Signature Bank was ultimately sold to Flagstar Bank. However, they were forced to spin out their digital asset-related accounts before doing so. This public signaling and sudden regulatory shift made clear that, at least as of the first quarter of 2023, the Federal Bank Regulatory Agencies would not tolerate banks with significant concentrations of digital asset customers, ultimately preventing Silvergate Bank from continuing its digital asset focused business model. Pretty damning if you ask me. Also, very frustrating and most definitely illegal. Elizabeth Warren and her gaggle of hall monitors across alphabet soup agencies and the Federal Reserve have been on one massive, unconstitutional, power trip for the last four years. They've besmirched bitcoin and those of us working hard to ensure that the United States of America leads the way forward as bitcoin adoption continues at every turn. Good people striving to make the world a better place. No one is a better example of this than Alan Lane, the former CEO of Silvergate Bank. I consider Alan a friend and feel supremely confident when I say that he is one of the nicest and thoughtful people I have met in this industry. A man who followed his passion to bring legitimacy and much needed banking services to an industry that the incumbents refused to touch. And he did bring legitimacy. As I explained earlier, Alan and his team understood the volatile nature of the industry and built their firm in a way that took this volatility into account. Silvergate did not fail, they were forced to shut down by Elizabeth Warren and her acolytes at the regulatory agencies. What's worse, Warren's vendetta against bitcoin and the digital asset industry incited the largest banking crisis this country had seen since 2008. Silvergate and Signature being taken behind the woodshed put everyone on their toes and bank runs started across the country. This led to the failure of First Republic, Silicon Valley Bank and a couple of smaller banks, forced the Fed to step in with their emergency BTFP program, and burdened taxpayers with $40B in FDIC costs that needed to be absorbed as a result. If it weren't for the bailouts things would have gotten completely out of control. All because Elizabeth Warren wants to live in a world in which we are forced to use CBDCs and unable to opt-in to bitcoin. The euthanasia of Silvergate and Signature are only the tip of the iceberg when it comes to Chokepoint 2.0. Caitlin Long and Custodia have been in a years long battle with the Federal Reserve to receive a Fed master account so that they can properly serve their customers. For those who are unaware, Custodia is a full-reserve bank that exist to serve bitcoin and digital asset businesses as well as other adjacent businesses like fintechs, banks and funds. Custodia is a chartered bank and special purpose depository institution that has built custody services so that customers can hold bitcoin within their bank accounts alongside their dollar accounts. Like Silvergate and Signature, Custodia has been singled out and unlawfully denied a master account with the Fed because the Federal Reserve doesn't want a bank like Custodia to exist. Either because they worry about the ramifications of the introduction of a full-reserve bank into a system dominated by fractional-reserve banks or they simply do not want to see bitcoin succeed. If we're being honest, it's probably a combination of the two. Despite what we, or anyone else, thinks about the potential effect a bank like Custodia could have on the market if it's granted a master account, the Fed's actions are unconstitutional in this case as well. This was made pretty clear (but yet to be determined by a court) in an amicus brief written by Paul Clement on behalf of Custodia earlier this Summer. The Fed is actively undermining the dual-banking system that was set up in this country to enable competition between state chartered banks and the Federal Reserve system. In the case of Custodia, the Federal Reserve is exhibiting expansive discretionary power that it has never shown before. Custodia is a state chartered special purpose depository institution in the state of Wyoming. Historically, it would be trivial for this type of state chartered bank to get a master account with the Fed. But for whatever reason (we know the reason) the Fed has been denying Custodia their right to this account for a number of years. To the point where Custodia was forced to sue the Federal Reserve and take their case to the courts. What's interesting about the saga of Custodia and the Fed is that it has forced Custodia's legal team to dig in and highlight where the Fed is overextending its reach and acting arbitrarily. In the amicus brief that was published in July of this year, Paul Clement argues that the way Federal Reserve Bank presidents are chosen is unconstitutional when you take into consideration the fact the these Fed branch presidents are unilaterally undermining state banking laws by denying master accounts. If they are going to unilaterally undermine state banking laws they need to be appointed by the President or an official acting on behalf of the Executive Branch. Federal Reserve Bank presidents aren't appointed by the President of the United States or any official acting with the authority of the Executive Branch. Instead, they are appointed by their boards, which are controlled by the privately held commercial banks who own them. The Federal Reserve system is clearly acting unconstitutionally when they deny Custodia from being assigned a master account. The people in power within the federal government and the Federal Reserve system are actively targeting the bitcoin and digital asset industry, acting extrajudicially and making a mockery of the rule of law in the United States. They are completely out of control and it is important that everyone who cares about the future of bitcoin in the United States and the future of the United States more broadly (even if you don't like bitcoin) speaks out and fights against these totalitarians as vehemently as possible. What they are doing is wrong. It's unconstitutional. And it is putting the future of our country at risk. If the federal government, the regulators and the Federal Reserve do not get out of the way and let law abiding citizens build the businesses they want and associate with businesses they want, those businesses will go elsewhere and the United States will be set back generations as a result. It's time to put these people in their place and let it be known that freedom will reign supreme in the Land of the Free. Fight! --- Final thought... I promised Parker Lewis that I would do cross fit on Friday morning and I'm using today's final thought as an accountability tool. @ c6f7077f:ad5d48fd
2024-09-08 01:24:03***“The more you learn about something, the more you realize you know nothing.”*** This saying resonates deeply with me. The truth is, **no one really has all the big answers**. Many in the scientific community seem to pretend they do. Let’s explore this further. #### ***Consider the Most Fundamental Questions*** 1. **The Origin of the Universe** 2. **The Origin of Life on Earth** #### ***The Origin of the Universe*** You might think we have a solid answer: **the Big Bang**. However, this explanation has its limitations, and calling it a “start” can be misleading. In fact, this theory might be entirely wrong. New research challenges the Big Bang theory, and I highly recommend listening to **Sir Roger Penrose** for a deeper understanding. The only substantial evidence we have is the universe's expansion. Penrose proposes a different hypothesis: **the endless expansion and contraction of the universe**. This idea doesn’t contradict our current understanding. Thus, the evidence for the Big Bang and Penrose’s theory are both radically different, yet **neither can be definitively proven** over the other. This highlights the **limitations of our current understanding**. #### ***The Origin of Life on Earth*** The origin of life is even more complex. Life requires three essential components: - **Proteins** for basic functioning - **RNA** for storing and replicating genes - **Lipids** (cell walls) to create separation from the environment Mathematical models suggest that while proteins and lipids have a reasonable probability of forming, the creation of RNA seems nearly impossible through random mutations in a short time frame. The best explanations indicate that we either lack crucial information or that these RNA molecules—and life as a whole—might have come from **outside sources**. Some scholars even question the entire **random mutation model**. #### ***The Question of Certainty*** If scientists don’t know the answers, **why do they pretend they do?** In my humble opinion, **It seems they do this to distance science from religion and to close the discussion before the wealthiest can fit God into the narrative,** Interestingly, I’m not alone in believing they closed the books too early. #### ***Reclaiming Control of Science and Education*** The best way to reclaim control of science and education is to **learn**. If you’re looking for a starting point, I highly recommend: - **“A Brief History of Time”** by **Stephen Hawking** for physics - **“Sapiens”** or **“The Selfish Gene”** for evolutionary biology All three are excellent starting points—densely packed with information and covering a wide range of topics in a concise and accessible manner.
@ c6f7077f:ad5d48fd
2024-09-08 01:24:03***“The more you learn about something, the more you realize you know nothing.”*** This saying resonates deeply with me. The truth is, **no one really has all the big answers**. Many in the scientific community seem to pretend they do. Let’s explore this further. #### ***Consider the Most Fundamental Questions*** 1. **The Origin of the Universe** 2. **The Origin of Life on Earth** #### ***The Origin of the Universe*** You might think we have a solid answer: **the Big Bang**. However, this explanation has its limitations, and calling it a “start” can be misleading. In fact, this theory might be entirely wrong. New research challenges the Big Bang theory, and I highly recommend listening to **Sir Roger Penrose** for a deeper understanding. The only substantial evidence we have is the universe's expansion. Penrose proposes a different hypothesis: **the endless expansion and contraction of the universe**. This idea doesn’t contradict our current understanding. Thus, the evidence for the Big Bang and Penrose’s theory are both radically different, yet **neither can be definitively proven** over the other. This highlights the **limitations of our current understanding**. #### ***The Origin of Life on Earth*** The origin of life is even more complex. Life requires three essential components: - **Proteins** for basic functioning - **RNA** for storing and replicating genes - **Lipids** (cell walls) to create separation from the environment Mathematical models suggest that while proteins and lipids have a reasonable probability of forming, the creation of RNA seems nearly impossible through random mutations in a short time frame. The best explanations indicate that we either lack crucial information or that these RNA molecules—and life as a whole—might have come from **outside sources**. Some scholars even question the entire **random mutation model**. #### ***The Question of Certainty*** If scientists don’t know the answers, **why do they pretend they do?** In my humble opinion, **It seems they do this to distance science from religion and to close the discussion before the wealthiest can fit God into the narrative,** Interestingly, I’m not alone in believing they closed the books too early. #### ***Reclaiming Control of Science and Education*** The best way to reclaim control of science and education is to **learn**. If you’re looking for a starting point, I highly recommend: - **“A Brief History of Time”** by **Stephen Hawking** for physics - **“Sapiens”** or **“The Selfish Gene”** for evolutionary biology All three are excellent starting points—densely packed with information and covering a wide range of topics in a concise and accessible manner. @ 460c25e6:ef85065c
2024-08-29 01:07:22If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one. ## Public Home/Outbox Relays Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, **they will not receive your updates**. Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience. This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to [relay.tools](https://relay.tools/) and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts. ## Public Inbox Relays This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out. Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience. This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to [nostr.watch](https://nostr.watch/relays/find) and find relays in your country Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here. ## DM Inbox Relays These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. **If you don't have it setup, you will miss DMs**. DM Inbox relays should accept any message from anyone, but only allow you to download them. Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy. Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a hidden, but public relay if you want DM notifications from our servers. Make sure to add at least one public relay if you want to see DM notifications. ## Private Home Relays Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools. Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa. ## Search relays: This is the list of relays to use on Amethyst's search and user tagging with @. **Tagging and searching will not work if there is nothing here.**. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com ## Local Relays: This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option. ## General Relays: This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each. Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible. Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them. ## My setup Here's what I use: 1. Go to [relay.tools](https://relay.tools/) and create a relay for yourself. 2. Go to [nostr.wine](https://nostr.wine/) and pay for their subscription. 3. Go to [inbox.nostr.wine](https://inbox.nostr.wine/) and pay for their subscription. 4. Go to [nostr.watch](https://nostr.watch/relays/find) and find a good relay in your country. 5. Download Citrine to your phone. Then, on your relay lists, put: Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. - <your.relay>.nostr1.com Public Inbox Relays - nos.lol or an in-country relay - <your.relay>.nostr1.com DM Inbox Relays - inbox.nostr.wine - <your.relay>.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) - <your.relay>.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com Local Relays - ws://localhost:4869 (Citrine) General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom And a few of the recommended relays from Amethyst. ## Final Considerations Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
@ 460c25e6:ef85065c
2024-08-29 01:07:22If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one. ## Public Home/Outbox Relays Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, **they will not receive your updates**. Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience. This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to [relay.tools](https://relay.tools/) and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts. ## Public Inbox Relays This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out. Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience. This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to [nostr.watch](https://nostr.watch/relays/find) and find relays in your country Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here. ## DM Inbox Relays These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. **If you don't have it setup, you will miss DMs**. DM Inbox relays should accept any message from anyone, but only allow you to download them. Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy. Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a hidden, but public relay if you want DM notifications from our servers. Make sure to add at least one public relay if you want to see DM notifications. ## Private Home Relays Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools. Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa. ## Search relays: This is the list of relays to use on Amethyst's search and user tagging with @. **Tagging and searching will not work if there is nothing here.**. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com ## Local Relays: This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option. ## General Relays: This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each. Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible. Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them. ## My setup Here's what I use: 1. Go to [relay.tools](https://relay.tools/) and create a relay for yourself. 2. Go to [nostr.wine](https://nostr.wine/) and pay for their subscription. 3. Go to [inbox.nostr.wine](https://inbox.nostr.wine/) and pay for their subscription. 4. Go to [nostr.watch](https://nostr.watch/relays/find) and find a good relay in your country. 5. Download Citrine to your phone. Then, on your relay lists, put: Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. - <your.relay>.nostr1.com Public Inbox Relays - nos.lol or an in-country relay - <your.relay>.nostr1.com DM Inbox Relays - inbox.nostr.wine - <your.relay>.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) - <your.relay>.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com Local Relays - ws://localhost:4869 (Citrine) General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom And a few of the recommended relays from Amethyst. ## Final Considerations Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies. @ da18e986:3a0d9851
2024-08-14 13:58:24After months of development I am excited to officially announce the first version of DVMDash (v0.1). DVMDash is a monitoring and debugging tool for all Data Vending Machine (DVM) activity on Nostr. The website is live at [https://dvmdash.live](https://dvmdash.live) and the code is available on [Github](https://github.com/dtdannen/dvmdash). Data Vending Machines ([NIP-90](https://github.com/nostr-protocol/nips/blob/master/90.md)) offload computationally expensive tasks from relays and clients in a decentralized, free-market manner. They are especially useful for AI tools, algorithmic processing of user’s feeds, and many other use cases. The long term goal of DVMDash is to become 1) a place to easily see what’s happening in the DVM ecosystem with metrics and graphs, and 2) provide real-time tools to help developers monitor, debug, and improve their DVMs. DVMDash aims to enable users to answer these types of questions at a glance: * What’s the most popular DVM right now? * How much money is being paid to image generation DVMs? * Is any DVM down at the moment? When was the last time that DVM completed a task? * Have any DVMs failed to deliver after accepting payment? Did they refund that payment? * How long does it take this DVM to respond? * For task X, what’s the average amount of time it takes for a DVM to complete the task? * … and more For developers working with DVMs there is now a visual, graph based tool that shows DVM-chain activity. DVMs have already started calling other DVMs to assist with work. Soon, we will have humans in the loop monitoring DVM activity, or completing tasks themselves. The activity trace of which DVM is being called as part of a sub-task from another DVM will become complicated, especially because these decisions will be made at run-time and are not known ahead of time. Building a tool to help users and developers understand where a DVM is in this activity trace, whether it’s gotten stuck or is just taking a long time, will be invaluable. *For now, the website only shows 1 step of a dvm chain from a user's request.* One of the main designs for the site is that it is highly _clickable_, meaning whenever you see a DVM, Kind, User, or Event ID, you can click it and open that up in a new page to inspect it. Another aspect of this website is that it should be fast. If you submit a DVM request, you should see it in DVMDash within seconds, as well as events from DVMs interacting with your request. I have attempted to obtain DVM events from relays as quickly as possible and compute metrics over them within seconds. This project makes use of a nosql database and graph database, currently set to use mongo db and neo4j, for which there are free, community versions that can be run locally. Finally, I’m grateful to nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f for supporting this project. ## Features in v0.1: ### Global Network Metrics: This page shows the following metrics: - **DVM Requests:** Number of unencrypted DVM requests (kind 5000-5999) - **DVM Results:** Number of unencrypted DVM results (kind 6000-6999) - **DVM Request Kinds Seen:** Number of unique kinds in the Kind range 5000-5999 (except for known non-DVM kinds 5666 and 5969) - **DVM Result Kinds Seen:** Number of unique kinds in the Kind range 6000-6999 (except for known non-DVM kinds 6666 and 6969) - **DVM Pub Keys Seen:** Number of unique pub keys that have written a kind 6000-6999 (except for known non-DVM kinds) or have published a kind 31990 event that specifies a ‘k’ tag value between 5000-5999 - **DVM Profiles (NIP-89) Seen**: Number of 31990 that have a ‘k’ tag value for kind 5000-5999 - **Most Popular DVM**: The DVM that has produced the most result events (kind 6000-6999) - **Most Popular Kind**: The Kind in range 5000-5999 that has the most requests by users. - **24 hr DVM Requests**: Number of kind 5000-5999 events created in the last 24 hrs - **24 hr DVM Results**: Number of kind 6000-6999 events created in the last 24 hours - **1 week DVM Requests**: Number of kind 5000-5999 events created in the last week - **1 week DVM Results**: Number of kind 6000-6999 events created in the last week - **Unique Users of DVMs**: Number of unique pubkeys of kind 5000-5999 events - **Total Sats Paid to DVMs**: - This is an estimate. - This value is likely a lower bound as it does not take into consideration subscriptions paid to DVMs - This is calculated by counting the values of all invoices where: - A DVM published a kind 7000 event requesting payment and containing an invoice - The DVM later provided a DVM Result for the same job for which it requested payment. - The assumption is that the invoice was paid, otherwise the DVM would not have done the work - Note that because there are multiple ways to pay a DVM such as lightning invoices, ecash, and subscriptions, there is no guaranteed way to know whether a DVM has been paid. Additionally, there is no way to know that a DVM completed the job because some DVMs may not publish a final result event and instead send the user a DM or take some other kind of action. ### Recent Requests: This page shows the most recent 3 events per kind, sorted by created date. You should always be able to find the last 3 events here of all DVM kinds. ### DVM Browser: This page will either show a profile of a specific DVM, or when no DVM is given in the url, it will show a table of all DVMs with some high level stats. Users can click on a DVM in the table to load the DVM specific page. ### Kind Browser: This page will either show data on a specific kind including all DVMs that have performed jobs of that kind, or when no kind is given, it will show a table summarizing activity across all Kinds. ### Debug: This page shows the graph based visualization of all events, users, and DVMs involved in a single job as well as a table of all events in order from oldest to newest. When no event is given, this page shows the 200 most recent events where the user can click on an event in order to debug that job. The graph-based visualization allows the user to zoom in and out and move around the graph, as well as double click on any node in the graph (except invoices) to open up that event, user, or dvm in a new page. ### Playground: This page is currently under development and may not work at the moment. If it does work, in the current state you can login with NIP-07 extension and broadcast a 5050 event with some text and then the page will show you events from DVMs. This page will be used to interact with DVMs live. A current good alternative to this feature, for some but not all kinds, is [https://vendata.io/](https://vendata.io/). ## Looking to the Future I originally built DVMDash out of Fear-of-Missing-Out (FOMO); I wanted to make AI systems that were comprised of DVMs but my day job was taking up a lot of my time. I needed to know when someone was performing a new task or launching a new AI or Nostr tool! I have a long list of DVMs and Agents I hope to build and I needed DVMDash to help me do it; I hope it helps you achieve your goals with Nostr, DVMs, and even AI. To this end, I wish for this tool to be useful to others, so if you would like a feature, please [submit a git issue here](https://github.com/dtdannen/dvmdash/issues/new) or _note_ me on Nostr! ### Immediate Next Steps: - Refactoring code and removing code that is no longer used - Improve documentation to run the project locally - Adding a metric for number of encrypted requests - Adding a metric for number of encrypted results ### Long Term Goals: - Add more metrics based on community feedback - Add plots showing metrics over time - Add support for showing a multi-dvm chain in the graph based visualizer - Add a real-time mode where the pages will auto update (currently the user must refresh the page) - ... Add support for user requested features! ## Acknowledgements There are some fantastic people working in the DVM space right now. Thank you to nostr:npub1drvpzev3syqt0kjrls50050uzf25gehpz9vgdw08hvex7e0vgfeq0eseet for making python bindings for nostr_sdk and for the recent asyncio upgrades! Thank you to nostr:npub1nxa4tywfz9nqp7z9zp7nr7d4nchhclsf58lcqt5y782rmf2hefjquaa6q8 for answering lots of questions about DVMs and for making the nostrdvm library. Thank you to nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft for making the original DVM NIP and [vendata.io](https://vendata.io/) which I use all the time for testing! P.S. I rushed to get this out in time for Nostriga 2024; code refactoring will be coming :)
@ da18e986:3a0d9851
2024-08-14 13:58:24After months of development I am excited to officially announce the first version of DVMDash (v0.1). DVMDash is a monitoring and debugging tool for all Data Vending Machine (DVM) activity on Nostr. The website is live at [https://dvmdash.live](https://dvmdash.live) and the code is available on [Github](https://github.com/dtdannen/dvmdash). Data Vending Machines ([NIP-90](https://github.com/nostr-protocol/nips/blob/master/90.md)) offload computationally expensive tasks from relays and clients in a decentralized, free-market manner. They are especially useful for AI tools, algorithmic processing of user’s feeds, and many other use cases. The long term goal of DVMDash is to become 1) a place to easily see what’s happening in the DVM ecosystem with metrics and graphs, and 2) provide real-time tools to help developers monitor, debug, and improve their DVMs. DVMDash aims to enable users to answer these types of questions at a glance: * What’s the most popular DVM right now? * How much money is being paid to image generation DVMs? * Is any DVM down at the moment? When was the last time that DVM completed a task? * Have any DVMs failed to deliver after accepting payment? Did they refund that payment? * How long does it take this DVM to respond? * For task X, what’s the average amount of time it takes for a DVM to complete the task? * … and more For developers working with DVMs there is now a visual, graph based tool that shows DVM-chain activity. DVMs have already started calling other DVMs to assist with work. Soon, we will have humans in the loop monitoring DVM activity, or completing tasks themselves. The activity trace of which DVM is being called as part of a sub-task from another DVM will become complicated, especially because these decisions will be made at run-time and are not known ahead of time. Building a tool to help users and developers understand where a DVM is in this activity trace, whether it’s gotten stuck or is just taking a long time, will be invaluable. *For now, the website only shows 1 step of a dvm chain from a user's request.* One of the main designs for the site is that it is highly _clickable_, meaning whenever you see a DVM, Kind, User, or Event ID, you can click it and open that up in a new page to inspect it. Another aspect of this website is that it should be fast. If you submit a DVM request, you should see it in DVMDash within seconds, as well as events from DVMs interacting with your request. I have attempted to obtain DVM events from relays as quickly as possible and compute metrics over them within seconds. This project makes use of a nosql database and graph database, currently set to use mongo db and neo4j, for which there are free, community versions that can be run locally. Finally, I’m grateful to nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f for supporting this project. ## Features in v0.1: ### Global Network Metrics: This page shows the following metrics: - **DVM Requests:** Number of unencrypted DVM requests (kind 5000-5999) - **DVM Results:** Number of unencrypted DVM results (kind 6000-6999) - **DVM Request Kinds Seen:** Number of unique kinds in the Kind range 5000-5999 (except for known non-DVM kinds 5666 and 5969) - **DVM Result Kinds Seen:** Number of unique kinds in the Kind range 6000-6999 (except for known non-DVM kinds 6666 and 6969) - **DVM Pub Keys Seen:** Number of unique pub keys that have written a kind 6000-6999 (except for known non-DVM kinds) or have published a kind 31990 event that specifies a ‘k’ tag value between 5000-5999 - **DVM Profiles (NIP-89) Seen**: Number of 31990 that have a ‘k’ tag value for kind 5000-5999 - **Most Popular DVM**: The DVM that has produced the most result events (kind 6000-6999) - **Most Popular Kind**: The Kind in range 5000-5999 that has the most requests by users. - **24 hr DVM Requests**: Number of kind 5000-5999 events created in the last 24 hrs - **24 hr DVM Results**: Number of kind 6000-6999 events created in the last 24 hours - **1 week DVM Requests**: Number of kind 5000-5999 events created in the last week - **1 week DVM Results**: Number of kind 6000-6999 events created in the last week - **Unique Users of DVMs**: Number of unique pubkeys of kind 5000-5999 events - **Total Sats Paid to DVMs**: - This is an estimate. - This value is likely a lower bound as it does not take into consideration subscriptions paid to DVMs - This is calculated by counting the values of all invoices where: - A DVM published a kind 7000 event requesting payment and containing an invoice - The DVM later provided a DVM Result for the same job for which it requested payment. - The assumption is that the invoice was paid, otherwise the DVM would not have done the work - Note that because there are multiple ways to pay a DVM such as lightning invoices, ecash, and subscriptions, there is no guaranteed way to know whether a DVM has been paid. Additionally, there is no way to know that a DVM completed the job because some DVMs may not publish a final result event and instead send the user a DM or take some other kind of action. ### Recent Requests: This page shows the most recent 3 events per kind, sorted by created date. You should always be able to find the last 3 events here of all DVM kinds. ### DVM Browser: This page will either show a profile of a specific DVM, or when no DVM is given in the url, it will show a table of all DVMs with some high level stats. Users can click on a DVM in the table to load the DVM specific page. ### Kind Browser: This page will either show data on a specific kind including all DVMs that have performed jobs of that kind, or when no kind is given, it will show a table summarizing activity across all Kinds. ### Debug: This page shows the graph based visualization of all events, users, and DVMs involved in a single job as well as a table of all events in order from oldest to newest. When no event is given, this page shows the 200 most recent events where the user can click on an event in order to debug that job. The graph-based visualization allows the user to zoom in and out and move around the graph, as well as double click on any node in the graph (except invoices) to open up that event, user, or dvm in a new page. ### Playground: This page is currently under development and may not work at the moment. If it does work, in the current state you can login with NIP-07 extension and broadcast a 5050 event with some text and then the page will show you events from DVMs. This page will be used to interact with DVMs live. A current good alternative to this feature, for some but not all kinds, is [https://vendata.io/](https://vendata.io/). ## Looking to the Future I originally built DVMDash out of Fear-of-Missing-Out (FOMO); I wanted to make AI systems that were comprised of DVMs but my day job was taking up a lot of my time. I needed to know when someone was performing a new task or launching a new AI or Nostr tool! I have a long list of DVMs and Agents I hope to build and I needed DVMDash to help me do it; I hope it helps you achieve your goals with Nostr, DVMs, and even AI. To this end, I wish for this tool to be useful to others, so if you would like a feature, please [submit a git issue here](https://github.com/dtdannen/dvmdash/issues/new) or _note_ me on Nostr! ### Immediate Next Steps: - Refactoring code and removing code that is no longer used - Improve documentation to run the project locally - Adding a metric for number of encrypted requests - Adding a metric for number of encrypted results ### Long Term Goals: - Add more metrics based on community feedback - Add plots showing metrics over time - Add support for showing a multi-dvm chain in the graph based visualizer - Add a real-time mode where the pages will auto update (currently the user must refresh the page) - ... Add support for user requested features! ## Acknowledgements There are some fantastic people working in the DVM space right now. Thank you to nostr:npub1drvpzev3syqt0kjrls50050uzf25gehpz9vgdw08hvex7e0vgfeq0eseet for making python bindings for nostr_sdk and for the recent asyncio upgrades! Thank you to nostr:npub1nxa4tywfz9nqp7z9zp7nr7d4nchhclsf58lcqt5y782rmf2hefjquaa6q8 for answering lots of questions about DVMs and for making the nostrdvm library. Thank you to nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft for making the original DVM NIP and [vendata.io](https://vendata.io/) which I use all the time for testing! P.S. I rushed to get this out in time for Nostriga 2024; code refactoring will be coming :) @ 30ceb64e:7f08bdf5
2024-08-14 11:51:36Heres a scenario: Imagine you have a nostr e-cash/Lightning Wallet and you would like to have a maximum receive balance of 20k split in between 5 mints that enable multipath payments. Pick 5 mints below to store 4k sats each, the funds are automatically withdrawn to your lightning node at the end of the day. Stacker News Robosats Sparrow Coinkite Start9 Rabbit Hole Recap @siggy47 Damus LND Your own mint originally posted at https://stacker.news/items/648298
@ 30ceb64e:7f08bdf5
2024-08-14 11:51:36Heres a scenario: Imagine you have a nostr e-cash/Lightning Wallet and you would like to have a maximum receive balance of 20k split in between 5 mints that enable multipath payments. Pick 5 mints below to store 4k sats each, the funds are automatically withdrawn to your lightning node at the end of the day. Stacker News Robosats Sparrow Coinkite Start9 Rabbit Hole Recap @siggy47 Damus LND Your own mint originally posted at https://stacker.news/items/648298 @ 30ceb64e:7f08bdf5
2024-08-14 11:15:27>It's wild. I just proved I can build #nostr 'wallet' where I can store the encrypted tokens in a Germany relay and make the lightning payment out of a Singapore mint. All using a #nsec that never leaves my machine. https://primal.net/e/note15l02rf4r474ck04mlrxxfagyl0z6t04ltsugf9dtph4xxhzfnd4sqpk74n >I’ve proven to myself that a #nostr wallet can exist across time and space, independently of any one app, server or custodian. The only thing which controls the ‘wallet’ is the generation and control of an #nsec which is free to exist within or flee any jurisdiction. >In my mind, this lays to rest the notion that a wallet needs to be an app, service, or anything that can be captured commercially or by the state. https://primal.net/e/note13nwsh852x9tfex2jade6vwymhhct8zussxr4zwy7uag24hjc9stq0xsxaf https://image.nostr.build/07dd1b56d6bb60b13cfe6c19d9384bc3ef198d01af4be9a5c544f791b80b746a.png >I am thinking about coining the term “nsac” to refer to a wallet-like thing that can exist on #nostr holding your valuable things, such as ecash tokens. I have already implemented a prototype #cashu ecash wallet which looks to be promising. >So you would have: #npub - your identity #nsec - your private key #nsac - your valuables >Your #nsac could be the same as your #nsec but better case is to generate as many #nsacs as required. >Happy to hear feedback! >For reference, what a ‘sac’ is in the biological sense: >A **sac** is a biological term referring to a pouch or cavity in an organism that is typically enclosed and may contain fluid, air, or other substances. Sacs can serve various functions depending on their location and role in the body, such as protecting a developing embryo, facilitating the exchange of gases in the lungs, or reducing friction between moving parts in joints https://primal.net/e/note1snj7y9m6f7lhfzkd2ujzqcvparpgddzmgcgwsgghqvkcyd0rkqhsmmlyla npub1q6mcr8tlr3l4gus3sfnw6772s7zae6hqncmw5wj27ejud5wcxf7q0nx7d5 Wild stuff freaks, will nostr become the best lightning/E-Cash wallet? Let me know what you think. originally posted at https://stacker.news/items/648270
@ 30ceb64e:7f08bdf5
2024-08-14 11:15:27>It's wild. I just proved I can build #nostr 'wallet' where I can store the encrypted tokens in a Germany relay and make the lightning payment out of a Singapore mint. All using a #nsec that never leaves my machine. https://primal.net/e/note15l02rf4r474ck04mlrxxfagyl0z6t04ltsugf9dtph4xxhzfnd4sqpk74n >I’ve proven to myself that a #nostr wallet can exist across time and space, independently of any one app, server or custodian. The only thing which controls the ‘wallet’ is the generation and control of an #nsec which is free to exist within or flee any jurisdiction. >In my mind, this lays to rest the notion that a wallet needs to be an app, service, or anything that can be captured commercially or by the state. https://primal.net/e/note13nwsh852x9tfex2jade6vwymhhct8zussxr4zwy7uag24hjc9stq0xsxaf https://image.nostr.build/07dd1b56d6bb60b13cfe6c19d9384bc3ef198d01af4be9a5c544f791b80b746a.png >I am thinking about coining the term “nsac” to refer to a wallet-like thing that can exist on #nostr holding your valuable things, such as ecash tokens. I have already implemented a prototype #cashu ecash wallet which looks to be promising. >So you would have: #npub - your identity #nsec - your private key #nsac - your valuables >Your #nsac could be the same as your #nsec but better case is to generate as many #nsacs as required. >Happy to hear feedback! >For reference, what a ‘sac’ is in the biological sense: >A **sac** is a biological term referring to a pouch or cavity in an organism that is typically enclosed and may contain fluid, air, or other substances. Sacs can serve various functions depending on their location and role in the body, such as protecting a developing embryo, facilitating the exchange of gases in the lungs, or reducing friction between moving parts in joints https://primal.net/e/note1snj7y9m6f7lhfzkd2ujzqcvparpgddzmgcgwsgghqvkcyd0rkqhsmmlyla npub1q6mcr8tlr3l4gus3sfnw6772s7zae6hqncmw5wj27ejud5wcxf7q0nx7d5 Wild stuff freaks, will nostr become the best lightning/E-Cash wallet? Let me know what you think. originally posted at https://stacker.news/items/648270 @ 76c71aae:3e29cafa
2024-08-13 04:30:00On social media and in the Nostr space in particular, there’s been a lot of debate about the idea of supporting deletion and editing of notes. Some people think they’re vital features to have, others believe that more honest and healthy social media will come from getting rid of these features. The discussion about these features quickly turns to the feasibility of completely deleting something on a decentralized protocol. We quickly get to the “We can’t really delete anything from the internet, or a decentralized network.” argument. This crowds out how Delete and Edit can mimic elements of offline interactions, how they can be used as social signals. When it comes to issues of deletion and editing content, what matters more is if the creator can communicate their intentions around their content. Sure, on the internet, with decentralized protocols, there’s no way to be sure something’s deleted. It’s not like taking a piece of paper and burning it. Computers make copies of things all the time, computers don’t like deleting things. In particular, distributed systems tend to use a Kafka architecture with immutable logs, it’s just easier to keep everything around, as deleting and reindexing is hard. Even if the software could be made to delete something, there’s always screenshots, or even pictures of screens. We can’t provably make something disappear. What we need to do in our software is clearly express intention. A delete is actually a kind of retraction. “I no longer want to associate myself with this content, please stop showing it to people as part of what I’ve published, stop highlighting it, stop sharing it.” Even if a relay or other server keeps a copy, and keeps sharing it, being able to clearly state “hello world, this thing I said, was a mistake, please get rid of it.” Just giving users the chance to say “I deleted this” is a way of showing intention. It’s also a way of signaling that feedback has been heard. Perhaps the post was factually incorrect or perhaps it was mean and the person wants to remove what they said. In an IRL conversation, for either of these scenarios there is some dialogue where the creator of the content is learning something and taking action based on what they’ve learned. Without delete or edit, there is no option to signal to the rest of the community that you have learned something because of how the content is structured today. On most platforms a reply or response stating one’s learning will be lost often in a deluge of replies on the original post and subsequent posts are often not seen especially when the original goes viral. By providing tools like delete and edit we give people a chance to signal that they have heard the feedback and taken action. The Nostr Protocol supports delete and expiring notes. It was one of the reasons we switched from secure scuttlebutt to build on Nostr. Our nos.social app offers delete and while we know that not all relays will honor this, we believe it’s important to provide social signaling tools as a means of making the internet more humane. We believe that the power to learn from each other is more important than the need to police through moral outrage which is how the current platforms and even some Nostr clients work today. It’s important that we don’t say Nostr doesn’t support delete. Not all apps need to support requesting a delete, some might want to call it a retraction. It is important that users know there is no way to enforce a delete and not all relays may honor their request. Edit is similar, although not as widely supported as delete. It’s a creator making a clear statement that they’ve created a new version of their content. Maybe it’s a spelling error, or a new version of the content, or maybe they’re changing it altogether. Freedom online means freedom to retract a statement, freedom to update a statement, freedom to edit your own content. By building on these freedoms, we’ll make Nostr a space where people feel empowered and in control of their own media.
@ 76c71aae:3e29cafa
2024-08-13 04:30:00On social media and in the Nostr space in particular, there’s been a lot of debate about the idea of supporting deletion and editing of notes. Some people think they’re vital features to have, others believe that more honest and healthy social media will come from getting rid of these features. The discussion about these features quickly turns to the feasibility of completely deleting something on a decentralized protocol. We quickly get to the “We can’t really delete anything from the internet, or a decentralized network.” argument. This crowds out how Delete and Edit can mimic elements of offline interactions, how they can be used as social signals. When it comes to issues of deletion and editing content, what matters more is if the creator can communicate their intentions around their content. Sure, on the internet, with decentralized protocols, there’s no way to be sure something’s deleted. It’s not like taking a piece of paper and burning it. Computers make copies of things all the time, computers don’t like deleting things. In particular, distributed systems tend to use a Kafka architecture with immutable logs, it’s just easier to keep everything around, as deleting and reindexing is hard. Even if the software could be made to delete something, there’s always screenshots, or even pictures of screens. We can’t provably make something disappear. What we need to do in our software is clearly express intention. A delete is actually a kind of retraction. “I no longer want to associate myself with this content, please stop showing it to people as part of what I’ve published, stop highlighting it, stop sharing it.” Even if a relay or other server keeps a copy, and keeps sharing it, being able to clearly state “hello world, this thing I said, was a mistake, please get rid of it.” Just giving users the chance to say “I deleted this” is a way of showing intention. It’s also a way of signaling that feedback has been heard. Perhaps the post was factually incorrect or perhaps it was mean and the person wants to remove what they said. In an IRL conversation, for either of these scenarios there is some dialogue where the creator of the content is learning something and taking action based on what they’ve learned. Without delete or edit, there is no option to signal to the rest of the community that you have learned something because of how the content is structured today. On most platforms a reply or response stating one’s learning will be lost often in a deluge of replies on the original post and subsequent posts are often not seen especially when the original goes viral. By providing tools like delete and edit we give people a chance to signal that they have heard the feedback and taken action. The Nostr Protocol supports delete and expiring notes. It was one of the reasons we switched from secure scuttlebutt to build on Nostr. Our nos.social app offers delete and while we know that not all relays will honor this, we believe it’s important to provide social signaling tools as a means of making the internet more humane. We believe that the power to learn from each other is more important than the need to police through moral outrage which is how the current platforms and even some Nostr clients work today. It’s important that we don’t say Nostr doesn’t support delete. Not all apps need to support requesting a delete, some might want to call it a retraction. It is important that users know there is no way to enforce a delete and not all relays may honor their request. Edit is similar, although not as widely supported as delete. It’s a creator making a clear statement that they’ve created a new version of their content. Maybe it’s a spelling error, or a new version of the content, or maybe they’re changing it altogether. Freedom online means freedom to retract a statement, freedom to update a statement, freedom to edit your own content. By building on these freedoms, we’ll make Nostr a space where people feel empowered and in control of their own media. @ 30ceb64e:7f08bdf5
2024-08-08 16:38:33SN and Nostr are a match made in heaven. Here are some thoughts on further integration: ## 1. Splash Zapvertising Integration Both SN and Nostr clients should consider integrating splash zapvertising features, similar to: - [ZapAdd](https://www.zapadd.com/) - [Zapper Nostrapps](https://zapper.nostrapps.org/) These platforms could charge a small fee for coordinating transactions, creating a new revenue stream while promoting content across the Nostr network. ## 2. Transforming SN Territories into Npubs Stacker News Territories have the potential to become more than just internal communities. By converting them into Npubs (Nostr public keys), we can expand their reach and engagement. A portion of the monthly territory fee could be allocated towards zapvertising the Npub/Territory to the wider Nostr ecosystem. Here's a visualization of how SN could interact with other Nostr platforms: https://image.nostr.build/3ba24a8db8bdca6a4cd32fc25139fead4512b783ceb4f94e505eeea21e8167e5.png ## Example: SN Music Territory Npub Let's consider how an SN Music Territory could function as an Npub: 1. **Automatic Crossposting**: Top daily content is shared to Satlantis, Fountain, and Damus. 2. **Zapvertising**: Promotes engagement, gains followers, and attracts zaps. 3. **Wide Engagement**: Users from Primal, Yakihonne, and Mastodons bridge can like, repost, and zap content. 4. **Referral System Integration**: Works really well with SN's new referral system. 5. **Content Aggregation**: All posts are automatically compiled into an SN Music Territory blog for wider public sharing. ## Benefits and Considerations While this approach may not immediately make territory ownership profitable, it offers several advantages: - Enhanced engagement across multiple platforms - Increased monetization opportunities - Simplified management for territory owners (no direct Nostr interaction required) - Expanded reach into the broader Nostr ecosystem By implementing these ideas, Stacker News can position itself as a central hub within the Nostr universe, facilitating content sharing and engagement across multiple platforms while providing value to both users and territory owners. It would also be cool to add.... something like shipyard autoposting something that will allow you to see comments Nostr comments on SN WOT scores and an option to use your unified balance nostr wallet. originally posted at https://stacker.news/items/640607
@ 30ceb64e:7f08bdf5
2024-08-08 16:38:33SN and Nostr are a match made in heaven. Here are some thoughts on further integration: ## 1. Splash Zapvertising Integration Both SN and Nostr clients should consider integrating splash zapvertising features, similar to: - [ZapAdd](https://www.zapadd.com/) - [Zapper Nostrapps](https://zapper.nostrapps.org/) These platforms could charge a small fee for coordinating transactions, creating a new revenue stream while promoting content across the Nostr network. ## 2. Transforming SN Territories into Npubs Stacker News Territories have the potential to become more than just internal communities. By converting them into Npubs (Nostr public keys), we can expand their reach and engagement. A portion of the monthly territory fee could be allocated towards zapvertising the Npub/Territory to the wider Nostr ecosystem. Here's a visualization of how SN could interact with other Nostr platforms: https://image.nostr.build/3ba24a8db8bdca6a4cd32fc25139fead4512b783ceb4f94e505eeea21e8167e5.png ## Example: SN Music Territory Npub Let's consider how an SN Music Territory could function as an Npub: 1. **Automatic Crossposting**: Top daily content is shared to Satlantis, Fountain, and Damus. 2. **Zapvertising**: Promotes engagement, gains followers, and attracts zaps. 3. **Wide Engagement**: Users from Primal, Yakihonne, and Mastodons bridge can like, repost, and zap content. 4. **Referral System Integration**: Works really well with SN's new referral system. 5. **Content Aggregation**: All posts are automatically compiled into an SN Music Territory blog for wider public sharing. ## Benefits and Considerations While this approach may not immediately make territory ownership profitable, it offers several advantages: - Enhanced engagement across multiple platforms - Increased monetization opportunities - Simplified management for territory owners (no direct Nostr interaction required) - Expanded reach into the broader Nostr ecosystem By implementing these ideas, Stacker News can position itself as a central hub within the Nostr universe, facilitating content sharing and engagement across multiple platforms while providing value to both users and territory owners. It would also be cool to add.... something like shipyard autoposting something that will allow you to see comments Nostr comments on SN WOT scores and an option to use your unified balance nostr wallet. originally posted at https://stacker.news/items/640607 @ f0aca767:dce3306e
2024-08-07 02:47:40A while back, I posted about The First Descendant and how, despite feeling clunky, and not really having satisfying gun play, it at _least_ seemed to have the ability to satisfy _more_ than Warframe. I _may_ have been wrong about that. I _may_ have sold Warframe a little short in being offered a new, shiny thing that lost its luster pretty damn quickly. So, let's talk about the shooter-grinder that _maybe_ started it all. This story goes back all the way to 2014, around a year after Warframe had originally released. I was dating a locksmith at the time. Not very integral to the story, because her being a locksmith has nothing to do with Warframe ... It was just, you know, the biggest thing I remember _about_ her (aside from, a year later, telling me she didn't think I was dating material). But, she was staying at my place, and I remember distinctly waking up in the morning to her, on _my_ PC, playing this weird ... ninja space game. It had almost no features, no story, and really all you did was click a mission, then shoot things, and then pick up some loot. Wash, rinse, _repeat_. There were no flying ship animations, no rotating solar maps, _nothing._ I got into it for about a week or so before I realized I couldn't really take playing a game that was technically in open beta, or even alpha? I don't remember. So, I dropped it. I would revisit it again and again, shooting things, leveling up, and then losing motivation. Until suddenly, one day, the star map was moving, and you could see the ship you were on flying _to those missions._ Amazing. But I kept going in and out of it like tossing out pairs of socks. At least until around 2016 when an online friend convinced me to join her, because there was some _ridiculous_ mission we had to do called "the Second Dream." Let's just say, it _blew me away_. Finally. A character creator? And, a **story? **Albeit, you're some kind of Stranger Things-esque powerful teenager who pilots these metal space ninjas, but it was _something_. Evangelion, maybe. I spent a week figuring out what all was new, ran around with my new human legs, found an open world _thing_ on Earth ... Yeah, I left the game again ... until 2018, and the Fortuna update. Needless to say, I was blown away, _again_. And, after getting frustrated that I couldn't just _have_ the cool new guns and my own hoverboard in a reasonable amount of time ... I left. This basically is the theme behind my relationship with Digital Extremes and Warframe. I'm the rubber-band player. Getting real excited about all the honestly really cool stuff, and revolutionary storytelling, and then having my motivation riddled with bullets and swords when faced with the prospect of having to spend time collecting things and grinding reputation. The cycle begins again. It's 2024, and I'm back in Warframe, enticed by some wild new expansion announcement that _apparently_ takes you back to ... [1999](https://www.warframe.com/1999)??? HUH? So, I'm swallowing the grind pill, and I'm doing it. Knocking every mission out, one by one, and I'm _almost_ to the New War.  But, here are my feelings about Warframe, all these years later. A space ninja MMO is freaking _awesome_. I have like, 20 different warframes, and some of them I've never even tried. I'm account level 8, almost 9, and I'm working on upgrading my own massive capital ship (called a Railjack). The story is gripping, wild, and probably some of the best writing I've _ever_ seen in a game, and I cannot _wait_ to get through to more recent content. But, despite swallowing that pill, and despite working through toward what I want, that's the one problem that remains with Warframe. The game absolutely **disrespects** your time as a human being. The Second War: Hey buddy, you need a Railjack and a Necramech before you can continue the story. Frikken' scrub. Okay, so I have the Railjack, in which you use to engage in space combat that isn't all that much unlike combat in No Man's Sky. But ... the Necramech? Oh ... Oh, you gotta grind a bunch of materials on the dead moon Deimos before you can build it? Queue the internal screaming. This is why I've left the game 40 times since 2014. I'm _not_ a fan of grinding. I have a full-time job, I have extracurricular things I like to do with my time. Spending hours upon hours collecting materials, so I can build a mech, so I can engage in yet another form of combat, so I can continue the _masterfully crafted_ storyline ... it seems to me like needless barriers to get to what you _actually_ want. The GAME. But, sure, I mean, yeah. They need hooks to keep you playing, because if you blast through the storyline, and you don't have to do anything else, you lose your player base. I just wish grinding didn't feel like I suddenly had a second job. But ... I'M GONNA DO IT. I'm not quitting this time. For real. If you wanna help me out, my account name is CMDR_N0va. My overall feelings on Warframe are that it's probably one of the best games _ever_ made, that kind of annoys the absolute _hell_ out of me ... at times.
@ f0aca767:dce3306e
2024-08-07 02:47:40A while back, I posted about The First Descendant and how, despite feeling clunky, and not really having satisfying gun play, it at _least_ seemed to have the ability to satisfy _more_ than Warframe. I _may_ have been wrong about that. I _may_ have sold Warframe a little short in being offered a new, shiny thing that lost its luster pretty damn quickly. So, let's talk about the shooter-grinder that _maybe_ started it all. This story goes back all the way to 2014, around a year after Warframe had originally released. I was dating a locksmith at the time. Not very integral to the story, because her being a locksmith has nothing to do with Warframe ... It was just, you know, the biggest thing I remember _about_ her (aside from, a year later, telling me she didn't think I was dating material). But, she was staying at my place, and I remember distinctly waking up in the morning to her, on _my_ PC, playing this weird ... ninja space game. It had almost no features, no story, and really all you did was click a mission, then shoot things, and then pick up some loot. Wash, rinse, _repeat_. There were no flying ship animations, no rotating solar maps, _nothing._ I got into it for about a week or so before I realized I couldn't really take playing a game that was technically in open beta, or even alpha? I don't remember. So, I dropped it. I would revisit it again and again, shooting things, leveling up, and then losing motivation. Until suddenly, one day, the star map was moving, and you could see the ship you were on flying _to those missions._ Amazing. But I kept going in and out of it like tossing out pairs of socks. At least until around 2016 when an online friend convinced me to join her, because there was some _ridiculous_ mission we had to do called "the Second Dream." Let's just say, it _blew me away_. Finally. A character creator? And, a **story? **Albeit, you're some kind of Stranger Things-esque powerful teenager who pilots these metal space ninjas, but it was _something_. Evangelion, maybe. I spent a week figuring out what all was new, ran around with my new human legs, found an open world _thing_ on Earth ... Yeah, I left the game again ... until 2018, and the Fortuna update. Needless to say, I was blown away, _again_. And, after getting frustrated that I couldn't just _have_ the cool new guns and my own hoverboard in a reasonable amount of time ... I left. This basically is the theme behind my relationship with Digital Extremes and Warframe. I'm the rubber-band player. Getting real excited about all the honestly really cool stuff, and revolutionary storytelling, and then having my motivation riddled with bullets and swords when faced with the prospect of having to spend time collecting things and grinding reputation. The cycle begins again. It's 2024, and I'm back in Warframe, enticed by some wild new expansion announcement that _apparently_ takes you back to ... [1999](https://www.warframe.com/1999)??? HUH? So, I'm swallowing the grind pill, and I'm doing it. Knocking every mission out, one by one, and I'm _almost_ to the New War.  But, here are my feelings about Warframe, all these years later. A space ninja MMO is freaking _awesome_. I have like, 20 different warframes, and some of them I've never even tried. I'm account level 8, almost 9, and I'm working on upgrading my own massive capital ship (called a Railjack). The story is gripping, wild, and probably some of the best writing I've _ever_ seen in a game, and I cannot _wait_ to get through to more recent content. But, despite swallowing that pill, and despite working through toward what I want, that's the one problem that remains with Warframe. The game absolutely **disrespects** your time as a human being. The Second War: Hey buddy, you need a Railjack and a Necramech before you can continue the story. Frikken' scrub. Okay, so I have the Railjack, in which you use to engage in space combat that isn't all that much unlike combat in No Man's Sky. But ... the Necramech? Oh ... Oh, you gotta grind a bunch of materials on the dead moon Deimos before you can build it? Queue the internal screaming. This is why I've left the game 40 times since 2014. I'm _not_ a fan of grinding. I have a full-time job, I have extracurricular things I like to do with my time. Spending hours upon hours collecting materials, so I can build a mech, so I can engage in yet another form of combat, so I can continue the _masterfully crafted_ storyline ... it seems to me like needless barriers to get to what you _actually_ want. The GAME. But, sure, I mean, yeah. They need hooks to keep you playing, because if you blast through the storyline, and you don't have to do anything else, you lose your player base. I just wish grinding didn't feel like I suddenly had a second job. But ... I'M GONNA DO IT. I'm not quitting this time. For real. If you wanna help me out, my account name is CMDR_N0va. My overall feelings on Warframe are that it's probably one of the best games _ever_ made, that kind of annoys the absolute _hell_ out of me ... at times. @ 30ceb64e:7f08bdf5
2024-08-05 20:14:03I feel sorry for the laggards who would pile into bitcoin at the last moment. They'll be fleeing into bitcoin through crypto scams, fake L2's, AI social engineering attacks, misinformation from trusted sources and cognitive dissonance. In a rapidly shifting open source environment niched in topics that they hardly understand. And at the bottom of the rabbit hole you have personal responsibility and hard work waiting for you. I'm assuming uncle jims will do well. They essentially become financial advisors (Recommending Bitcoin products and services, Helping them understand and move up the sovereignty ladder, Holding Keys, Running LSP's, Mints, and Relays). Its just crazy to imagine that we're entering a world were 20 year olds have a better grasp on how to use money, how money works, and why it works that way.....than most studied economics professionals. Understanding money is a key piece to human flourishing and survival, many will succumb to being slaves of their own ignorance, doomed to live out the rest of their days as hungry ghosts, pulling knobs and levers of which have no real meaning or consequence. https://cdn.satellite.earth/40f7fa81b77c2097ee499cd63d47e66b245aedb20d9a782f33622427c5179dab.webp originally posted at https://stacker.news/items/636597
@ 30ceb64e:7f08bdf5
2024-08-05 20:14:03I feel sorry for the laggards who would pile into bitcoin at the last moment. They'll be fleeing into bitcoin through crypto scams, fake L2's, AI social engineering attacks, misinformation from trusted sources and cognitive dissonance. In a rapidly shifting open source environment niched in topics that they hardly understand. And at the bottom of the rabbit hole you have personal responsibility and hard work waiting for you. I'm assuming uncle jims will do well. They essentially become financial advisors (Recommending Bitcoin products and services, Helping them understand and move up the sovereignty ladder, Holding Keys, Running LSP's, Mints, and Relays). Its just crazy to imagine that we're entering a world were 20 year olds have a better grasp on how to use money, how money works, and why it works that way.....than most studied economics professionals. Understanding money is a key piece to human flourishing and survival, many will succumb to being slaves of their own ignorance, doomed to live out the rest of their days as hungry ghosts, pulling knobs and levers of which have no real meaning or consequence. https://cdn.satellite.earth/40f7fa81b77c2097ee499cd63d47e66b245aedb20d9a782f33622427c5179dab.webp originally posted at https://stacker.news/items/636597 @ 3c984938:2ec11289
2024-07-22 11:43:17## Bienvenide a Nostr! **Introduccíon** Es tu primera vez aqui en Nostr? Bienvenides! Nostr es un acrónimo raro para "Notes and Other Stuff Transmitted by Relays" on un solo objetivo; resistirse a la censura. Una alternativa a las redes sociales tradicionales, comunicaciónes, blogging, streaming, podcasting, y feventualmente el correo electronico (en fase de desarrollo) con características descentralizadas que te capacita, usario. Jamas seras molestado por un anuncio, capturado por una entidad centralizada o algoritmo que te monetiza. Permítame ser su anfitrión! Soy Onigiri! Yo estoy explorando el mundo de Nostr, un protocolo de comunicacíon decentralizada. Yo escribo sobre las herramientas y los desarolladores increíbles de Nostr que dan vida a esta reino.  ## Bienvenides a Nostr Wonderland Estas a punto de entrar a un otro mundo digtal que te hará explotar tu mente de todas las aplicaciones descentralizadas, clientes, sitios que puedes utilizar. Nunca volverás a ver a las comunicaciones ni a las redes sociales de la mesma manera. Todo gracias al carácter criptográfico de nostr, inpirado por la tecnología "blockchain". Cada usario, cuando crean una cuenta en Nostr, recibe un par de llaves: una privada y una publico. Estos son las llaves de tu propio reino. Lo que escribes, cantes, grabes, lo que creas - todo te pertenece.  ### Unos llaves de Oro y Plata Mi amigo y yo llamamos a esto "identidad mediante cifrado" porque tu identidad es cifrado. Tu puedes compartir tu llave de plata "npub" a otros usarios para conectar y seguir. Utiliza tu llave de oro "nsec" para accedar a tu cuenta y exponerte a muchas aplicaciones. Mantenga la llave a buen recaudo en todo momento. Ya no hay razor para estar enjaulado por los terminos de plataformas sociales nunca más. Onigirl ``` npub18jvyjwpmm65g8v9azmlvu8knd5m7xlxau08y8vt75n53jtkpz2ys6mqqu3 ``` ### Todavia No tienes un cliente? Seleccione la mejor opción. Encuentra la aplicación adecuada para ti! Utilice su clave de oro "nsec" para acceder a estas herramientas maravillosas. También puedes visit a esta pagina a ver a todas las aplicaciones. Antes de pegar tu llave de oro en muchas aplicaciones, considera un "signer" (firmante) para los sitios web 3. Por favor, mire la siguiente imagen para más detalles. Consulte también la leyenda. 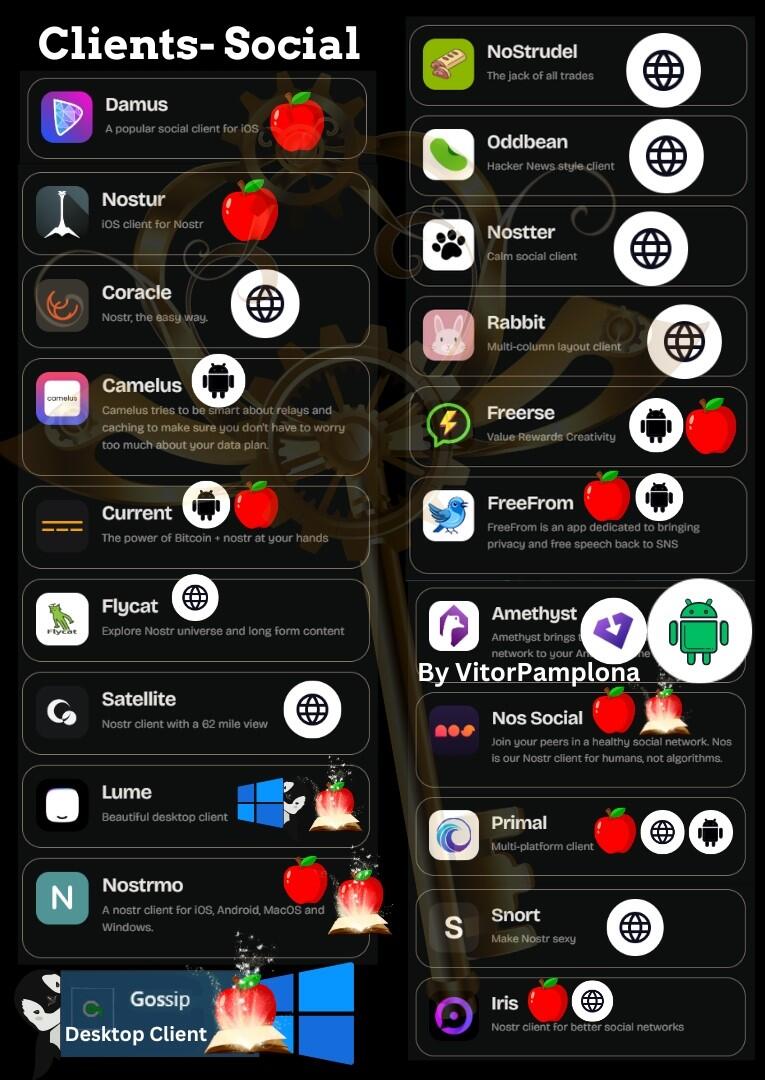 ### Get a Signer extension via chrome webstore Un firmante (o "signer" en inglés) es una extensión del navegador web. Nos2x and NostrConnect son extensiónes ampliamente aceptado para aceder a Nostr. Esto simplifica el proceso de aceder a sitios "web 3". En lugar de copiar y pegar la clave oro "nsec" cada vez, la mantienes guardado en la extensión y le des permiso para aceder a Nostr.  ### 👉⚡⚡Obtén una billetera Bitcoin lightning para enviar/recibir Zaps⚡⚡ (Esto es opcional)  Aqui en Nostr, utilizamos la red Lightning de Bitcoin (L2). Nesitaras una cartera lightning para enviar y recibir Satoshis, la denominacion mas chiquita de un Bitcoin. (0.000000001 BTC) Los "zaps" son un tipo de micropago en Nostr. Si te gusta el contenido de un usario, es norma dejarle una propina en la forma de un ¨zap". Por ejemplo, si te gusta este contenido, tu me puedes hacer "zap" con Satoshis para recompensar mi trabajo. Pero apenas llegaste, as que todavia no tienes una cartera. No se preocupe, puedo ayudar en eso! "[Stacker.News](https://stacker.news/r/Hamstr)" es una plataforma donde los usarios pueden ganar SATS por publicar articulos y interactuar con otros.  Stacker.News es el lugar mas facil para recibir una direccion de cartera Bitcoin Lightning. 1. Acedese con su extensión firmante "signer" - Nos2x or NostrConnect - hace click en tu perfil, un codigo de letras y numeros en la mano superior derecha. Veás algo como esto  2. Haga clic en "edit" y elija un nombre que te guste. Se puede cambiar si deseas en el futuro.  3. Haga clic en "save" 4. Crea una biografía y la comunidad SN son muy acogedora. Te mandarán satoshi para darte la bienvenida. 5. Tu nueva direccion de cartera Bitcoin Lightning aparecerá asi  **^^No le mandas "zaps" a esta direccion; es puramente con fines educativos.** 6. Con tu **Nueva** dirección de monedero Bitcoin Lightning puedes ponerla en cualquier cliente o app de tu elección. Para ello, ve a tu **página de perfil** y bajo la dirección de tu monedero en "**Dirección Lightning**", introduce tu nueva dirección y pulsa **"guardar "** y ya está. Enhorabuena. 👉✨Con el tiempo, es posible que desee pasar a las opciones de auto-custodia y tal vez incluso considerar la posibilidad de auto-alojar su propio nodo LN para una mejor privacidad. La buena noticia es que stacker.news tambien está dejando de ser una cartera custodio. ⭐NIP-05-identidad DNS⭐ Al igual que en Twitter, una marca de verificación es para mostrar que eres del mismo jardín "como un humano", y no un atípico como una mala hierba o, "bot". Pero no de la forma nefasta en que lo hacen las grandes tecnológicas. En el país de las maravillas de Nostr, esto te permite asignar tu llave de plata, "npub", a un identificador DNS. Una vez verificado, puedes gritar para anunciar tu nueva residencia Nostr para compartir. ✨Hay un montón de opciones, pero si has seguido los pasos, esto se vuelve extremadamente fácil. 👉✅¡Haz clic en tu **"Perfil "**, luego en **"Configuración "**, desplázate hasta la parte inferior y pega tu *clave Silver*, **"npub!"** y haz clic en **"Guardar "** y ¡listo! Utiliza tu monedero relámpago de Stacker.news como tu NIP-05. ¡¡¡Enhorabuena!!! ¡Ya estás verificado! Dale unas horas y cuando uses tu cliente **"principal "** deberías ver una marca de verificación. ### Nostr, el infonformista de los servidores. 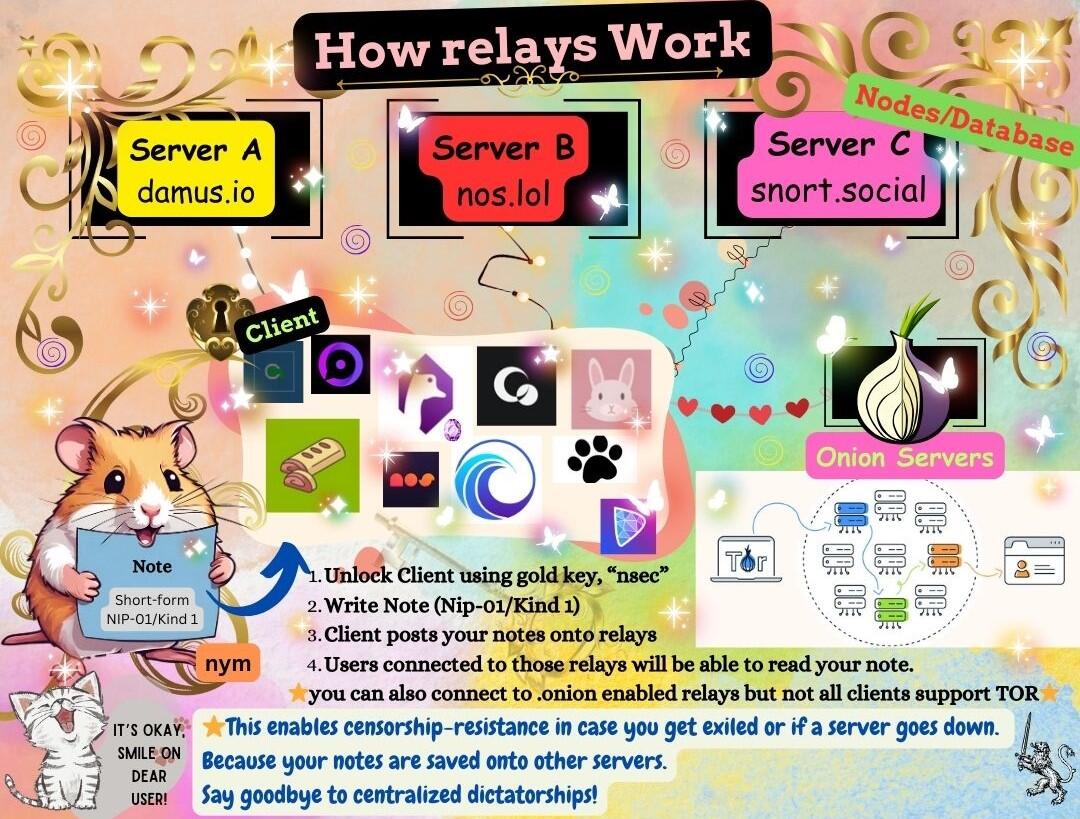 En lugar de utilizar una única instancia o un servidor centralizado, Nostr está construido para que varias bases de datos intercambien mensajes mediante "relés". Los relés, que son neutrales y no discriminatorios, almacenan y difunden mensajes públicos en la red Nostr. Transmiten mensajes a todos los demás clientes conectados a ellos, asegurando las comunicaciones en la red descentralizada. ### ¡Mis amigos en Nostr te dan la bienvenida! Bienvenida a la fiesta. ¿Le apetece un té?🍵  ### ¡Hay mucho mas! Esto es la punta del iceberg. Síguenme mientras continúo explorando nuevas tierras y a los desarolladores, los caballeres que potencioan este ecosistema. Encuéntrame aquí para mas contenido como este y comparten con otros usarios de nostr. Conozca a los caballeres que luchan por freedomTech (la tecnología de libertad) en Nostr y a los proyectos a los que contribuyen para hacerla realidad.💋 Onigirl @npub18jvyjwpmm65g8v9azmlvu8knd5m7xlxau08y8vt75n53jtkpz2ys6mqqu3 ---- 🧡😻Esta guía ha sido cuidadosamente traducida por miggymofongo Puede seguirla aquí. @npub1ajt9gp0prf4xrp4j07j9rghlcyukahncs0fw5ywr977jccued9nqrcc0cs sitio [web](https://miguelalmodo.com/)
@ 3c984938:2ec11289
2024-07-22 11:43:17## Bienvenide a Nostr! **Introduccíon** Es tu primera vez aqui en Nostr? Bienvenides! Nostr es un acrónimo raro para "Notes and Other Stuff Transmitted by Relays" on un solo objetivo; resistirse a la censura. Una alternativa a las redes sociales tradicionales, comunicaciónes, blogging, streaming, podcasting, y feventualmente el correo electronico (en fase de desarrollo) con características descentralizadas que te capacita, usario. Jamas seras molestado por un anuncio, capturado por una entidad centralizada o algoritmo que te monetiza. Permítame ser su anfitrión! Soy Onigiri! Yo estoy explorando el mundo de Nostr, un protocolo de comunicacíon decentralizada. Yo escribo sobre las herramientas y los desarolladores increíbles de Nostr que dan vida a esta reino.  ## Bienvenides a Nostr Wonderland Estas a punto de entrar a un otro mundo digtal que te hará explotar tu mente de todas las aplicaciones descentralizadas, clientes, sitios que puedes utilizar. Nunca volverás a ver a las comunicaciones ni a las redes sociales de la mesma manera. Todo gracias al carácter criptográfico de nostr, inpirado por la tecnología "blockchain". Cada usario, cuando crean una cuenta en Nostr, recibe un par de llaves: una privada y una publico. Estos son las llaves de tu propio reino. Lo que escribes, cantes, grabes, lo que creas - todo te pertenece.  ### Unos llaves de Oro y Plata Mi amigo y yo llamamos a esto "identidad mediante cifrado" porque tu identidad es cifrado. Tu puedes compartir tu llave de plata "npub" a otros usarios para conectar y seguir. Utiliza tu llave de oro "nsec" para accedar a tu cuenta y exponerte a muchas aplicaciones. Mantenga la llave a buen recaudo en todo momento. Ya no hay razor para estar enjaulado por los terminos de plataformas sociales nunca más. Onigirl ``` npub18jvyjwpmm65g8v9azmlvu8knd5m7xlxau08y8vt75n53jtkpz2ys6mqqu3 ``` ### Todavia No tienes un cliente? Seleccione la mejor opción. Encuentra la aplicación adecuada para ti! Utilice su clave de oro "nsec" para acceder a estas herramientas maravillosas. También puedes visit a esta pagina a ver a todas las aplicaciones. Antes de pegar tu llave de oro en muchas aplicaciones, considera un "signer" (firmante) para los sitios web 3. Por favor, mire la siguiente imagen para más detalles. Consulte también la leyenda. 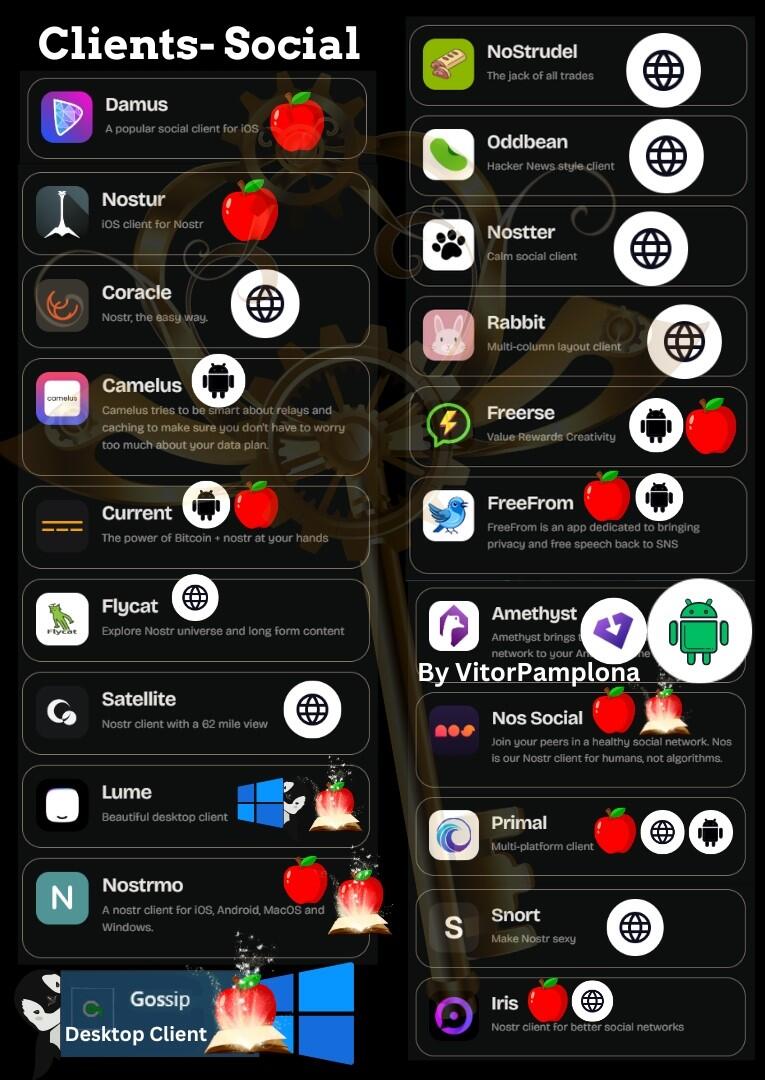 ### Get a Signer extension via chrome webstore Un firmante (o "signer" en inglés) es una extensión del navegador web. Nos2x and NostrConnect son extensiónes ampliamente aceptado para aceder a Nostr. Esto simplifica el proceso de aceder a sitios "web 3". En lugar de copiar y pegar la clave oro "nsec" cada vez, la mantienes guardado en la extensión y le des permiso para aceder a Nostr.  ### 👉⚡⚡Obtén una billetera Bitcoin lightning para enviar/recibir Zaps⚡⚡ (Esto es opcional)  Aqui en Nostr, utilizamos la red Lightning de Bitcoin (L2). Nesitaras una cartera lightning para enviar y recibir Satoshis, la denominacion mas chiquita de un Bitcoin. (0.000000001 BTC) Los "zaps" son un tipo de micropago en Nostr. Si te gusta el contenido de un usario, es norma dejarle una propina en la forma de un ¨zap". Por ejemplo, si te gusta este contenido, tu me puedes hacer "zap" con Satoshis para recompensar mi trabajo. Pero apenas llegaste, as que todavia no tienes una cartera. No se preocupe, puedo ayudar en eso! "[Stacker.News](https://stacker.news/r/Hamstr)" es una plataforma donde los usarios pueden ganar SATS por publicar articulos y interactuar con otros.  Stacker.News es el lugar mas facil para recibir una direccion de cartera Bitcoin Lightning. 1. Acedese con su extensión firmante "signer" - Nos2x or NostrConnect - hace click en tu perfil, un codigo de letras y numeros en la mano superior derecha. Veás algo como esto  2. Haga clic en "edit" y elija un nombre que te guste. Se puede cambiar si deseas en el futuro.  3. Haga clic en "save" 4. Crea una biografía y la comunidad SN son muy acogedora. Te mandarán satoshi para darte la bienvenida. 5. Tu nueva direccion de cartera Bitcoin Lightning aparecerá asi  **^^No le mandas "zaps" a esta direccion; es puramente con fines educativos.** 6. Con tu **Nueva** dirección de monedero Bitcoin Lightning puedes ponerla en cualquier cliente o app de tu elección. Para ello, ve a tu **página de perfil** y bajo la dirección de tu monedero en "**Dirección Lightning**", introduce tu nueva dirección y pulsa **"guardar "** y ya está. Enhorabuena. 👉✨Con el tiempo, es posible que desee pasar a las opciones de auto-custodia y tal vez incluso considerar la posibilidad de auto-alojar su propio nodo LN para una mejor privacidad. La buena noticia es que stacker.news tambien está dejando de ser una cartera custodio. ⭐NIP-05-identidad DNS⭐ Al igual que en Twitter, una marca de verificación es para mostrar que eres del mismo jardín "como un humano", y no un atípico como una mala hierba o, "bot". Pero no de la forma nefasta en que lo hacen las grandes tecnológicas. En el país de las maravillas de Nostr, esto te permite asignar tu llave de plata, "npub", a un identificador DNS. Una vez verificado, puedes gritar para anunciar tu nueva residencia Nostr para compartir. ✨Hay un montón de opciones, pero si has seguido los pasos, esto se vuelve extremadamente fácil. 👉✅¡Haz clic en tu **"Perfil "**, luego en **"Configuración "**, desplázate hasta la parte inferior y pega tu *clave Silver*, **"npub!"** y haz clic en **"Guardar "** y ¡listo! Utiliza tu monedero relámpago de Stacker.news como tu NIP-05. ¡¡¡Enhorabuena!!! ¡Ya estás verificado! Dale unas horas y cuando uses tu cliente **"principal "** deberías ver una marca de verificación. ### Nostr, el infonformista de los servidores. 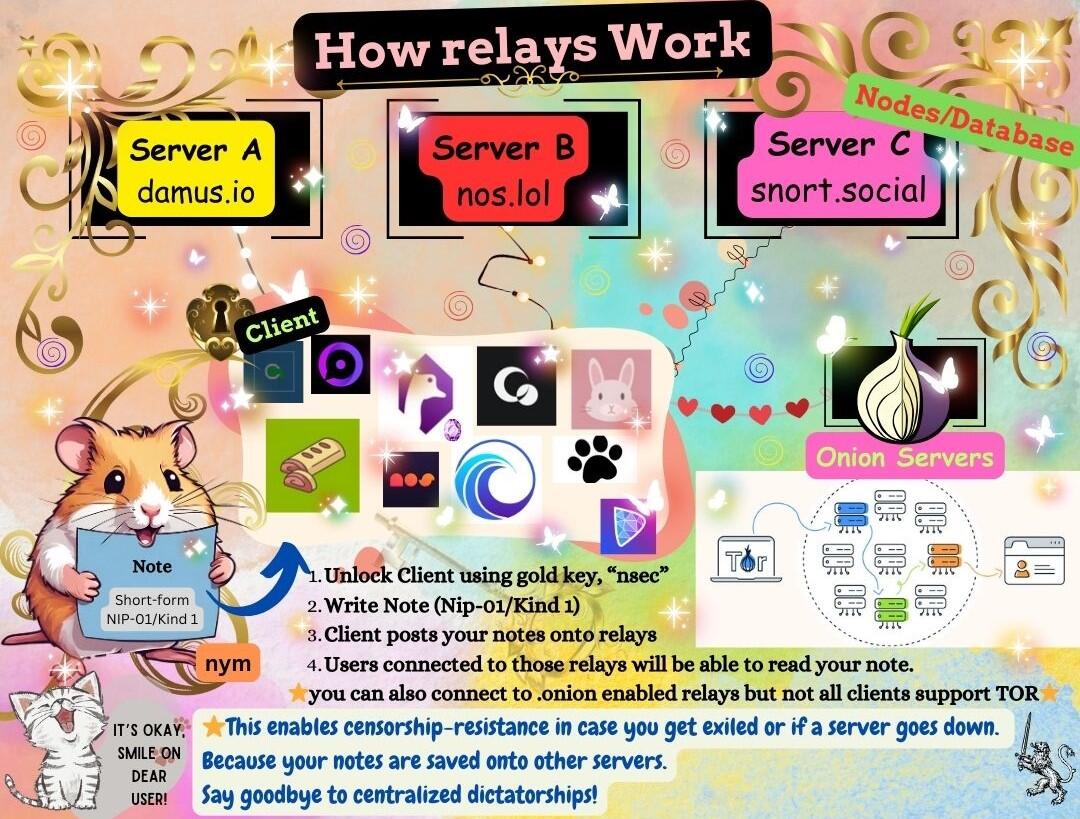 En lugar de utilizar una única instancia o un servidor centralizado, Nostr está construido para que varias bases de datos intercambien mensajes mediante "relés". Los relés, que son neutrales y no discriminatorios, almacenan y difunden mensajes públicos en la red Nostr. Transmiten mensajes a todos los demás clientes conectados a ellos, asegurando las comunicaciones en la red descentralizada. ### ¡Mis amigos en Nostr te dan la bienvenida! Bienvenida a la fiesta. ¿Le apetece un té?🍵  ### ¡Hay mucho mas! Esto es la punta del iceberg. Síguenme mientras continúo explorando nuevas tierras y a los desarolladores, los caballeres que potencioan este ecosistema. Encuéntrame aquí para mas contenido como este y comparten con otros usarios de nostr. Conozca a los caballeres que luchan por freedomTech (la tecnología de libertad) en Nostr y a los proyectos a los que contribuyen para hacerla realidad.💋 Onigirl @npub18jvyjwpmm65g8v9azmlvu8knd5m7xlxau08y8vt75n53jtkpz2ys6mqqu3 ---- 🧡😻Esta guía ha sido cuidadosamente traducida por miggymofongo Puede seguirla aquí. @npub1ajt9gp0prf4xrp4j07j9rghlcyukahncs0fw5ywr977jccued9nqrcc0cs sitio [web](https://miguelalmodo.com/) @ 20986fb8:cdac21b3
2024-07-02 21:08:21The motivation of building decentralized media protocols is to balance the power of centralized media platforms, and provide an alternative for the public to take part in the curation of information, not just access information. It has to perform checks-and-balances to the centralized media powers, while providing a credible and neutral mechanism for different communities to improve a platform over time. The operation and maintenance of such a media platform should be autonomous, unstoppable, and self-improving. While a traditional media platform has to align itself with the interests of its owners, shareholders, and donors, the new type of media platform should not be subject to the control of any entity at all times. The ownership and stewardship of the new media platform should be open and transparent to the public. This is in contrast to state/corporate-controlled media platforms, in which case the public is often not informed of a media platform’s real ownership and stewardship, hence the public cannot be aware of its real purpose, bias, and hidden agendas. If each individual is more informed, it will be harder to manipulate public opinions, and it will be easier to foster independent judgment within human societies. The positive externality will be enormous. The transition from centralized media platforms to decentralized media platforms speeds up this process. This article discusses the two pillars to implement a decentralized media technology stack: decentralized publication and decentralized content moderation. # Decentralization of publication In a previous article, we extensively discussed the importance of content decentralization. It is the last defense of censorship - content removed or hidden by popular client websites could be stored permanently and be displayed on other (perhaps non-popular) client websites. We also discussed the importance of token economics neutrality, because token economics itself could lead to censorship. As a non-microblogging platform, [Yakihonne](https://yakihonne.com) is currently one of the most popular clients that implemented [NIP-23](https://github.com/nostr-protocol/nips/blob/master/23.md), attracting bloggers and readers from all over the world to post articles and read contents about Bitcoin and beyond. > **As of the time of writing of this article, the platform serves users in 116 countries, supporting 18 languages, and has become the most widely used and feature-rich client within the Nostr ecosystem. Yakihonne is also the first Nostr client to support mobile applications and article editing on mobile apps.**  *When publishing articles on Yakihonne.com, you can choose multiple relays to publish the content. Relays can also implement logic to sync articles of their own interests and offer them to clients.* Joining the relay network is easy. If someone wants to join the relay network, he is able to do so by deploying one of the open source versions of Nostr relays, and starting to store content for the network. The number of relays serving content within the Nostr protocol is currently quite small. Over the next period of time, it is important to grow the number of reliable relays. It should be economically viable and encouraging to set up a relay, so that the number of relays can grow over time. Very likely, the number of relays will correspond to the net income of the network, which comes from revenue streams of each of the clients. Therefore, it is foreseeable that the number of reliable relays will be correlated to the traffic of the Nostr protocol in general and therefore, to the traffic of popular clients. The zap feature (Lightning Zaps) can be used to incentivize relays. But we cannot set unrealistic expectations over zapping. Zapping an article is making a donation. Donation is unpredictable, and it is definitely not a sustainable way to maintain a large, reliable network of relays. One possible solution to this problem is to have profitable clients make continuous contributions to well-performing relays via enforceable protocol setups.  *An ideal incentive mechanism for a relay network is to establish a profit-sharing protocol between clients and the relays.* # Decentralization of content moderation and content curation Striking a balance between moderation and anti-moderation has been an almost impossible task for centralized media platforms. Whoever performs the moderation dominates the narratives. The most recent [community notes](https://communitynotes.twitter.com/guide/en/about/introduction) feature on X took a major step towards community-driven moderation. In community notes, users who are eligible to provide notes can write community notes to a post, and a community can vote for the notes so that the best recognized notes can emerge on the top. It has been proven to be effective in content moderation in many instances, and the ability to add community-backed notes reduced the need for shadow bans.  *Community notes are obviously a more effective system than shadow bans in Jack Dorsey’s Twitter era. At times even Elon Musk himself can be “community noted” is definitely making people trust this system more.* But it cannot be ignored that users still have to sign up to apply for eligibility for community notes. It is in X's own direction to decide who is eligible and who is not. The voting process of community notes itself could also be subject to censorship, because there is no way to verify the votes. **This is to say, X has the power to do evil, it doesn’t matter if it does evil or not.** The countermeasure to balance the power of a centralized media platform is a platform that is not manipulatable by its operating team or share/token holders. So content moderation has to be permissionless, while verifiability to content moderation mechanisms like community notes. The first step to developing a decentralized content moderation system is to implement a permissionless community notes system.  *X’s community notes can be censored in two steps: the eligibility review process can filter people based on X’s own preference; the ranking and displaying rules are also controlled by X. In a permissionless community notes system, any relay or even client should be able to implement its own version of community notes, and users can choose their preferred system(s) to work with.* Notes have to be stored on an open, token economics neutral relay network to ensure their immutability and resistance to censorship. Community members can add notes to any media content, and the notes are distributed to non-related parties who operate the nodes. ## Incentives The content moderation mechanism needs to be incentivized through the decentralized media protocol. In a non-sponsored model, income comes from ads or subscription fees, and is distributed to content creators, content relays, and additional network security providers.  In a sponsored model, income is from content sponsors, and further distributed to community note contributors, content relays, and additional network security providers. A sponsored post, in old media platforms, can be quite expensive. The cost to post sponsored content can be dramatically reduced on a decentralized media platform because of the great reduction of content moderation cost.  ## Ranking Community notes can be ranked by either relays or clients. A content relay can rank community notes based on its own preference, and deliver to clients. Clients can also rank community notes based on its rules. Basically, **everyone can rank any post’s community notes.** In general, community notes ranking algorithms can be stake-based or non-stake based. Stake-based ranking algorithms in general show how people who have a stake in something react to a post. Non-stake based ranking algorithms can be any mechanism, such as reputation-weighted ranks, 1p1v ranks, quadratic voting ranks, random selection, or even asking an AI to rank community notes. What’s perhaps important is not which ranking algorithm is the best, it’s the flexibility for both the content storage layer and the interfaces (clients) to choose their ideal ranking algorithms. Probably for a client, the best strategy is to provide all ranks from multiple sources, so that people can view community notes from very different angles. # The Current Status of Bitcoin and the Nostr Protocol As Nostr is the ideal relay network for decentralized media at this moment, it is necessary to write some notes on the current status of the Bitcoin ecosystem, as Nostr is largely inspired by the Bitcoin network to be decentralized, and is greatly supported by the Bitcoin community. The Bitcoin community is so far the most legitimate crypto community. It has a very simple mission: to create a decentralized monetary system that is not controlled by centralized powers. The progressive element of the Bitcoin community is relative to the old banking world, where Bitcoin is a completely new and alternative technology stack to the centralized money and finance systems. The conservative element of the Bitcoin community is relative to the other crypto community, where the Bitcoin community is largely skeptical of the motivation and decentralization of them. In my opinion, the scrutiny Bitcoin community puts upon the rest of the crypto world is totally reasonable. However, as much as Nostr is inspired by the Bitcoin network, it will also go beyond the Bitcoin community, in terms of content. This is not a bad thing! If this happens on a big monolithic blockchain, probably the Nostr major contributors will be required to create a token pretty soon and then pay gas fees to the blockchain so that the blockchain’s revenue can increase. The Bitcoin community will never ask that. This gives Nostr enough freedom and flexibility to evolve, while continuously getting support from the Bitcoin community. However, if Nostr users are forever a subset of Bitcoin users, Nostr will be limited. Nostr is not a subset of Bitcoin, it is not an “ecosystem project” of Bitcoin either (a.k.a., it should not become a “layer-2” of Bitcoin, as some people reason about the future of Bitcoin totally from the analogy of Ethereum).  *In the best world, Nostr and Bitcoin can expand each other’s user base, and create healthy synergy.* # Conclusion Yakihonne is, so far, not a protocol. With the products and features it offers, Yakihonne is ready to build up a decentralized media stack. The stack has two pillars : decentralized publication and decentralized content moderation. The former guarantees that content will never be lost; the latter creates a new cost-incentive model to make sure that when content and moderation go permissionless, the platform can still maintain truthfulness and cost-effectiveness. In fact, a decentralized media platform can be more cost-effective than centralized media platforms. So the next step for us is to build this up and experiment with it. The Flash News and the uncensored notes are introduced for such purpose, and everyone is welcomed to give it a try. Note that it is still in the early stages and various improvements will come eventually, for this your feedback is valuable to us to reach any expectations.
@ 20986fb8:cdac21b3
2024-07-02 21:08:21The motivation of building decentralized media protocols is to balance the power of centralized media platforms, and provide an alternative for the public to take part in the curation of information, not just access information. It has to perform checks-and-balances to the centralized media powers, while providing a credible and neutral mechanism for different communities to improve a platform over time. The operation and maintenance of such a media platform should be autonomous, unstoppable, and self-improving. While a traditional media platform has to align itself with the interests of its owners, shareholders, and donors, the new type of media platform should not be subject to the control of any entity at all times. The ownership and stewardship of the new media platform should be open and transparent to the public. This is in contrast to state/corporate-controlled media platforms, in which case the public is often not informed of a media platform’s real ownership and stewardship, hence the public cannot be aware of its real purpose, bias, and hidden agendas. If each individual is more informed, it will be harder to manipulate public opinions, and it will be easier to foster independent judgment within human societies. The positive externality will be enormous. The transition from centralized media platforms to decentralized media platforms speeds up this process. This article discusses the two pillars to implement a decentralized media technology stack: decentralized publication and decentralized content moderation. # Decentralization of publication In a previous article, we extensively discussed the importance of content decentralization. It is the last defense of censorship - content removed or hidden by popular client websites could be stored permanently and be displayed on other (perhaps non-popular) client websites. We also discussed the importance of token economics neutrality, because token economics itself could lead to censorship. As a non-microblogging platform, [Yakihonne](https://yakihonne.com) is currently one of the most popular clients that implemented [NIP-23](https://github.com/nostr-protocol/nips/blob/master/23.md), attracting bloggers and readers from all over the world to post articles and read contents about Bitcoin and beyond. > **As of the time of writing of this article, the platform serves users in 116 countries, supporting 18 languages, and has become the most widely used and feature-rich client within the Nostr ecosystem. Yakihonne is also the first Nostr client to support mobile applications and article editing on mobile apps.**  *When publishing articles on Yakihonne.com, you can choose multiple relays to publish the content. Relays can also implement logic to sync articles of their own interests and offer them to clients.* Joining the relay network is easy. If someone wants to join the relay network, he is able to do so by deploying one of the open source versions of Nostr relays, and starting to store content for the network. The number of relays serving content within the Nostr protocol is currently quite small. Over the next period of time, it is important to grow the number of reliable relays. It should be economically viable and encouraging to set up a relay, so that the number of relays can grow over time. Very likely, the number of relays will correspond to the net income of the network, which comes from revenue streams of each of the clients. Therefore, it is foreseeable that the number of reliable relays will be correlated to the traffic of the Nostr protocol in general and therefore, to the traffic of popular clients. The zap feature (Lightning Zaps) can be used to incentivize relays. But we cannot set unrealistic expectations over zapping. Zapping an article is making a donation. Donation is unpredictable, and it is definitely not a sustainable way to maintain a large, reliable network of relays. One possible solution to this problem is to have profitable clients make continuous contributions to well-performing relays via enforceable protocol setups.  *An ideal incentive mechanism for a relay network is to establish a profit-sharing protocol between clients and the relays.* # Decentralization of content moderation and content curation Striking a balance between moderation and anti-moderation has been an almost impossible task for centralized media platforms. Whoever performs the moderation dominates the narratives. The most recent [community notes](https://communitynotes.twitter.com/guide/en/about/introduction) feature on X took a major step towards community-driven moderation. In community notes, users who are eligible to provide notes can write community notes to a post, and a community can vote for the notes so that the best recognized notes can emerge on the top. It has been proven to be effective in content moderation in many instances, and the ability to add community-backed notes reduced the need for shadow bans.  *Community notes are obviously a more effective system than shadow bans in Jack Dorsey’s Twitter era. At times even Elon Musk himself can be “community noted” is definitely making people trust this system more.* But it cannot be ignored that users still have to sign up to apply for eligibility for community notes. It is in X's own direction to decide who is eligible and who is not. The voting process of community notes itself could also be subject to censorship, because there is no way to verify the votes. **This is to say, X has the power to do evil, it doesn’t matter if it does evil or not.** The countermeasure to balance the power of a centralized media platform is a platform that is not manipulatable by its operating team or share/token holders. So content moderation has to be permissionless, while verifiability to content moderation mechanisms like community notes. The first step to developing a decentralized content moderation system is to implement a permissionless community notes system.  *X’s community notes can be censored in two steps: the eligibility review process can filter people based on X’s own preference; the ranking and displaying rules are also controlled by X. In a permissionless community notes system, any relay or even client should be able to implement its own version of community notes, and users can choose their preferred system(s) to work with.* Notes have to be stored on an open, token economics neutral relay network to ensure their immutability and resistance to censorship. Community members can add notes to any media content, and the notes are distributed to non-related parties who operate the nodes. ## Incentives The content moderation mechanism needs to be incentivized through the decentralized media protocol. In a non-sponsored model, income comes from ads or subscription fees, and is distributed to content creators, content relays, and additional network security providers.  In a sponsored model, income is from content sponsors, and further distributed to community note contributors, content relays, and additional network security providers. A sponsored post, in old media platforms, can be quite expensive. The cost to post sponsored content can be dramatically reduced on a decentralized media platform because of the great reduction of content moderation cost.  ## Ranking Community notes can be ranked by either relays or clients. A content relay can rank community notes based on its own preference, and deliver to clients. Clients can also rank community notes based on its rules. Basically, **everyone can rank any post’s community notes.** In general, community notes ranking algorithms can be stake-based or non-stake based. Stake-based ranking algorithms in general show how people who have a stake in something react to a post. Non-stake based ranking algorithms can be any mechanism, such as reputation-weighted ranks, 1p1v ranks, quadratic voting ranks, random selection, or even asking an AI to rank community notes. What’s perhaps important is not which ranking algorithm is the best, it’s the flexibility for both the content storage layer and the interfaces (clients) to choose their ideal ranking algorithms. Probably for a client, the best strategy is to provide all ranks from multiple sources, so that people can view community notes from very different angles. # The Current Status of Bitcoin and the Nostr Protocol As Nostr is the ideal relay network for decentralized media at this moment, it is necessary to write some notes on the current status of the Bitcoin ecosystem, as Nostr is largely inspired by the Bitcoin network to be decentralized, and is greatly supported by the Bitcoin community. The Bitcoin community is so far the most legitimate crypto community. It has a very simple mission: to create a decentralized monetary system that is not controlled by centralized powers. The progressive element of the Bitcoin community is relative to the old banking world, where Bitcoin is a completely new and alternative technology stack to the centralized money and finance systems. The conservative element of the Bitcoin community is relative to the other crypto community, where the Bitcoin community is largely skeptical of the motivation and decentralization of them. In my opinion, the scrutiny Bitcoin community puts upon the rest of the crypto world is totally reasonable. However, as much as Nostr is inspired by the Bitcoin network, it will also go beyond the Bitcoin community, in terms of content. This is not a bad thing! If this happens on a big monolithic blockchain, probably the Nostr major contributors will be required to create a token pretty soon and then pay gas fees to the blockchain so that the blockchain’s revenue can increase. The Bitcoin community will never ask that. This gives Nostr enough freedom and flexibility to evolve, while continuously getting support from the Bitcoin community. However, if Nostr users are forever a subset of Bitcoin users, Nostr will be limited. Nostr is not a subset of Bitcoin, it is not an “ecosystem project” of Bitcoin either (a.k.a., it should not become a “layer-2” of Bitcoin, as some people reason about the future of Bitcoin totally from the analogy of Ethereum).  *In the best world, Nostr and Bitcoin can expand each other’s user base, and create healthy synergy.* # Conclusion Yakihonne is, so far, not a protocol. With the products and features it offers, Yakihonne is ready to build up a decentralized media stack. The stack has two pillars : decentralized publication and decentralized content moderation. The former guarantees that content will never be lost; the latter creates a new cost-incentive model to make sure that when content and moderation go permissionless, the platform can still maintain truthfulness and cost-effectiveness. In fact, a decentralized media platform can be more cost-effective than centralized media platforms. So the next step for us is to build this up and experiment with it. The Flash News and the uncensored notes are introduced for such purpose, and everyone is welcomed to give it a try. Note that it is still in the early stages and various improvements will come eventually, for this your feedback is valuable to us to reach any expectations. @ 6871d8df:4a9396c1
2024-06-12 22:10:51# Embracing AI: A Case for AI Accelerationism In an era where artificial intelligence (AI) development is at the forefront of technological innovation, a counter-narrative championed by a group I refer to as the 'AI Decels'—those advocating for the deceleration of AI advancements— seems to be gaining significant traction. After tuning into a recent episode of the [Joe Rogan Podcast](https://fountain.fm/episode/0V35t9YBkOMVM4WRVLYp), I realized that the prevailing narrative around AI was heading in a dangerous direction. Rogan had Aza Raskin and Tristan Harris, technology safety advocates, who released a talk called '[The AI Dilemma](https://www.youtube.com/watch?v=xoVJKj8lcNQ),' on for a discussion. You may know them from the popular documentary '[The Social Dilemma](https://www.thesocialdilemma.com/)' on the dangers of social media. It became increasingly clear that the cautionary stance dominating this discourse might be tipping the scales too far, veering towards an over-regulated future that stifles innovation rather than fostering it.  ## Are we moving too fast? While acknowledging AI's benefits, Aza and Tristan fear it could be dangerous if not guided by ethical standards and safeguards. They believe AI development is moving too quickly and that the right incentives for its growth are not in place. They are concerned about the possibility of "civilizational overwhelm," where advanced AI technology far outpaces 21st-century governance. They fear a scenario where society and its institutions cannot manage or adapt to the rapid changes and challenges introduced by AI. They argue for regulating and slowing down AI development due to rapid, uncontrolled advancement driven by competition among companies like Google, OpenAI, and Microsoft. They claim this race can lead to unsafe releases of new technologies, with AI systems exhibiting unpredictable, emergent behaviors, posing significant societal risks. For instance, AI can inadvertently learn tasks like sentiment analysis or human emotion understanding, creating potential for misuse in areas like biological weapons or cybersecurity vulnerabilities. Moreover, AI companies' profit-driven incentives often conflict with the public good, prioritizing market dominance over safety and ethics. This misalignment can lead to technologies that maximize engagement or profits at societal expense, similar to the negative impacts seen with social media. To address these issues, they suggest government regulation to realign AI companies' incentives with safety, ethical considerations, and public welfare. Implementing responsible development frameworks focused on long-term societal impacts is essential for mitigating potential harm. ## This isn't new Though the premise of their concerns seems reasonable, it's dangerous and an all too common occurrence with the emergence of new technologies. For example, in their example in the podcast, they refer to the technological breakthrough of oil. Oil as energy was a technological marvel and changed the course of human civilization. The embrace of oil — now the cornerstone of industry in our age — revolutionized how societies operated, fueled economies, and connected the world in unprecedented ways. Yet recently, as ideas of its environmental and geopolitical ramifications propagated, the narrative around oil has shifted. Tristan and Aza detail this shift and claim that though the period was great for humanity, we didn't have another technology to go to once the technological consequences became apparent. The problem with that argument is that we did innovate to a better alternative: nuclear. However, at its technological breakthrough, it was met with severe suspicions, from safety concerns to ethical debates over its use. This overregulation due to these concerns caused a decades-long stagnation in nuclear innovation, where even today, we are still stuck with heavy reliance on coal and oil. The scare tactics and fear-mongering had consequences, and, interestingly, they don't see the parallels with their current deceleration stance on AI. These examples underscore a critical insight: the initial anxiety surrounding new technologies is a natural response to the unknowns they introduce. Yet, history shows that too much anxiety can stifle the innovation needed to address the problems posed by current technologies. The cycle of discovery, fear, adaptation, and eventual acceptance reveals an essential truth—progress requires not just the courage to innovate but also the resilience to navigate the uncertainties these innovations bring. Moreover, believing we can predict and plan for all AI-related unknowns reflects overconfidence in our understanding and foresight. History shows that technological progress, marked by unexpected outcomes and discoveries, defies such predictions. The evolution from the printing press to the internet underscores progress's unpredictability. Hence, facing AI's future requires caution, curiosity, and humility. Acknowledging our limitations and embracing continuous learning and adaptation will allow us to harness AI's potential responsibly, illustrating that embracing our uncertainties, rather than pretending to foresee them, is vital to innovation. The journey of technological advancement is fraught with both promise and trepidation. Historically, each significant leap forward, from the dawn of the industrial age to the digital revolution, has been met with a mix of enthusiasm and apprehension. Aza Raskin and Tristan Harris's thesis in the 'AI Dilemma' embodies the latter. ## Who defines "safe?" When slowing down technologies for safety or ethical reasons, the issue arises of who gets to define what "safe" or “ethical” mean? This inquiry is not merely technical but deeply ideological, touching the very core of societal values and power dynamics. For example, the push for Diversity, Equity, and Inclusion (DEI) initiatives shows how specific ideological underpinnings can shape definitions of safety and decency. Take the case of the initial release of Google's AI chatbot, Gemini, which chose the ideology of its creators over truth. Luckily, the answers were so ridiculous that the pushback was sudden and immediate. My worry, however, is if, in correcting this, they become experts in making the ideological capture much more subtle. Large bureaucratic institutions' top-down safety enforcement creates a fertile ground for ideological capture of safety standards.  I claim that the issue is not the technology itself but the lens through which we view and regulate it. Suppose the gatekeepers of 'safety' are aligned with a singular ideology. In that case, AI development would skew to serve specific ends, sidelining diverse perspectives and potentially stifling innovative thought and progress. In the podcast, Tristan and Aza suggest such manipulation as a solution. They propose using AI for consensus-building and creating "shared realities" to address societal challenges. In practice, this means that when individuals' viewpoints seem to be far apart, we can leverage AI to "bridge the gap." How they bridge the gap and what we would bridge it toward is left to the imagination, but to me, it is clear. Regulators will inevitably influence it from the top down, which, in my opinion, would be the opposite of progress. In navigating this terrain, we must advocate for a pluralistic approach to defining safety, encompassing various perspectives and values achieved through market forces rather than a governing entity choosing winners. The more players that can play the game, the more wide-ranging perspectives will catalyze innovation to flourish. ## Ownership & Identity Just because we should accelerate AI forward does not mean I do not have my concerns. When I think about what could be the most devastating for society, I don't believe we have to worry about a Matrix-level dystopia; I worry about freedom. As I explored in "[Whose data is it anyway?](https://cwilbzz.com/whose-data-is-it-anyway/)," my concern gravitates toward the issues of data ownership and the implications of relinquishing control over our digital identities. This relinquishment threatens our privacy and the integrity of the content we generate, leaving it susceptible to the inclinations and profit of a few dominant tech entities. To counteract these concerns, a paradigm shift towards decentralized models of data ownership is imperative. Such standards would empower individuals with control over their digital footprints, ensuring that we develop AI systems with diverse, honest, and truthful perspectives rather than the massaged, narrow viewpoints of their creators. This shift safeguards individual privacy and promotes an ethical framework for AI development that upholds the principles of fairness and impartiality. As we stand at the crossroads of technological innovation and ethical consideration, it is crucial to advocate for systems that place data ownership firmly in the hands of users. By doing so, we can ensure that the future of AI remains truthful, non-ideological, and aligned with the broader interests of society. ## But what about the Matrix? I know I am in the minority on this, but I feel that the concerns of AGI (Artificial General Intelligence) are generally overblown. I am not scared of reaching the point of AGI, and I think the idea that AI will become so intelligent that we will lose control of it is unfounded and silly. Reaching AGI is not reaching consciousness; being worried about it spontaneously gaining consciousness is a misplaced fear. It is a tool created by humans for humans to enhance productivity and achieve specific outcomes. At a technical level, large language models (LLMs) are trained on extensive datasets and learning patterns from language and data through a technique called "unsupervised learning" (meaning the data is untagged). They predict the next word in sentences, refining their predictions through feedback to improve coherence and relevance. When queried, LLMs generate responses based on learned patterns, simulating an understanding of language to provide contextually appropriate answers. They will only answer based on the datasets that were inputted and scanned. AI will never be "alive," meaning that AI lacks inherent agency, consciousness, and the characteristics of life, not capable of independent thought or action. AI cannot act independently of human control. Concerns about AI gaining autonomy and posing a threat to humanity are based on a misunderstanding of the nature of AI and the fundamental differences between living beings and machines. AI spontaneously developing a will or consciousness is more similar to thinking a hammer will start walking than us being able to create consciousness through programming. Right now, there is only one way to create consciousness, and I'm skeptical that is ever something we will be able to harness and create as humans. Irrespective of its complexity — and yes, our tools will continue to become evermore complex — machines, specifically AI, cannot transcend their nature as non-living, inanimate objects programmed and controlled by humans.  The advancement of AI should be seen as enhancing human capabilities, not as a path toward creating autonomous entities with their own wills. So, while AI will continue to evolve, improve, and become more powerful, I believe it will remain under human direction and control without the existential threats often sensationalized in discussions about AI's future. With this framing, we should not view the race toward AGI as something to avoid. This will only make the tools we use more powerful, making us more productive. With all this being said, AGI is still much farther away than many believe. Today's AI excels in specific, narrow tasks, known as narrow or weak AI. These systems operate within tightly defined parameters, achieving remarkable efficiency and accuracy that can sometimes surpass human performance in those specific tasks. Yet, this is far from the versatile and adaptable functionality that AGI represents. Moreover, the exponential growth of computational power observed in the past decades does not directly translate to an equivalent acceleration in achieving AGI. AI's impressive feats are often the result of massive data inputs and computing resources tailored to specific tasks. These successes do not inherently bring us closer to understanding or replicating the general problem-solving capabilities of the human mind, which again would only make the tools more potent in _our_ hands. While AI will undeniably introduce challenges and change the aspects of conflict and power dynamics, these challenges will primarily stem from humans wielding this powerful tool rather than the technology itself. AI is a mirror reflecting our own biases, values, and intentions. The crux of future AI-related issues lies not in the technology's inherent capabilities but in how it is used by those wielding it. This reality is at odds with the idea that we should slow down development as our biggest threat will come from those who are not friendly to us. ## AI Beget's AI While the unknowns of AI development and its pitfalls indeed stir apprehension, it's essential to recognize the power of market forces and human ingenuity in leveraging AI to address these challenges. History is replete with examples of new technologies raising concerns, only for those very technologies to provide solutions to the problems they initially seemed to exacerbate. It looks silly and unfair to think of fighting a war with a country that never embraced oil and was still primarily getting its energy from burning wood.  The evolution of AI is no exception to this pattern. As we venture into uncharted territories, the potential issues that arise with AI—be it ethical concerns, use by malicious actors, biases in decision-making, or privacy intrusions—are not merely obstacles but opportunities for innovation. It is within the realm of possibility, and indeed, probability, that AI will play a crucial role in solving the problems it creates. The idea that there would be no incentive to address and solve these problems is to underestimate the fundamental drivers of technological progress. Market forces, fueled by the demand for better, safer, and more efficient solutions, are powerful catalysts for positive change. When a problem is worth fixing, it invariably attracts the attention of innovators, researchers, and entrepreneurs eager to solve it. This dynamic has driven progress throughout history, and AI is poised to benefit from this problem-solving cycle. Thus, rather than viewing AI's unknowns as sources of fear, we should see them as sparks of opportunity. By tackling the challenges posed by AI, we will harness its full potential to benefit humanity. By fostering an ecosystem that encourages exploration, innovation, and problem-solving, we can ensure that AI serves as a force for good, solving problems as profound as those it might create. This is the optimism we must hold onto—a belief in our collective ability to shape AI into a tool that addresses its own challenges and elevates our capacity to solve some of society's most pressing issues. ## An AI Future The reality is that it isn't whether AI will lead to unforeseen challenges—it undoubtedly will, as has every major technological leap in history. The real issue is whether we let fear dictate our path and confine us to a standstill or embrace AI's potential to address current and future challenges. The approach to solving potential AI-related problems with stringent regulations and a slowdown in innovation is akin to cutting off the nose to spite the face. It's a strategy that risks stagnating the U.S. in a global race where other nations will undoubtedly continue their AI advancements. This perspective dangerously ignores that AI, much like the printing press of the past, has the power to democratize information, empower individuals, and dismantle outdated power structures. The way forward is not less AI but more of it, more innovation, optimism, and curiosity for the remarkable technological breakthroughs that will come. We must recognize that the solution to AI-induced challenges lies not in retreating but in advancing our capabilities to innovate and adapt. AI represents a frontier of limitless possibilities. If wielded with foresight and responsibility, it's a tool that can help solve some of the most pressing issues we face today. There are certainly challenges ahead, but I trust that with problems come solutions. Let's keep the AI Decels from steering us away from this path with their doomsday predictions. Instead, let's embrace AI with the cautious optimism it deserves, forging a future where technology and humanity advance to heights we can't imagine.
@ 6871d8df:4a9396c1
2024-06-12 22:10:51# Embracing AI: A Case for AI Accelerationism In an era where artificial intelligence (AI) development is at the forefront of technological innovation, a counter-narrative championed by a group I refer to as the 'AI Decels'—those advocating for the deceleration of AI advancements— seems to be gaining significant traction. After tuning into a recent episode of the [Joe Rogan Podcast](https://fountain.fm/episode/0V35t9YBkOMVM4WRVLYp), I realized that the prevailing narrative around AI was heading in a dangerous direction. Rogan had Aza Raskin and Tristan Harris, technology safety advocates, who released a talk called '[The AI Dilemma](https://www.youtube.com/watch?v=xoVJKj8lcNQ),' on for a discussion. You may know them from the popular documentary '[The Social Dilemma](https://www.thesocialdilemma.com/)' on the dangers of social media. It became increasingly clear that the cautionary stance dominating this discourse might be tipping the scales too far, veering towards an over-regulated future that stifles innovation rather than fostering it.  ## Are we moving too fast? While acknowledging AI's benefits, Aza and Tristan fear it could be dangerous if not guided by ethical standards and safeguards. They believe AI development is moving too quickly and that the right incentives for its growth are not in place. They are concerned about the possibility of "civilizational overwhelm," where advanced AI technology far outpaces 21st-century governance. They fear a scenario where society and its institutions cannot manage or adapt to the rapid changes and challenges introduced by AI. They argue for regulating and slowing down AI development due to rapid, uncontrolled advancement driven by competition among companies like Google, OpenAI, and Microsoft. They claim this race can lead to unsafe releases of new technologies, with AI systems exhibiting unpredictable, emergent behaviors, posing significant societal risks. For instance, AI can inadvertently learn tasks like sentiment analysis or human emotion understanding, creating potential for misuse in areas like biological weapons or cybersecurity vulnerabilities. Moreover, AI companies' profit-driven incentives often conflict with the public good, prioritizing market dominance over safety and ethics. This misalignment can lead to technologies that maximize engagement or profits at societal expense, similar to the negative impacts seen with social media. To address these issues, they suggest government regulation to realign AI companies' incentives with safety, ethical considerations, and public welfare. Implementing responsible development frameworks focused on long-term societal impacts is essential for mitigating potential harm. ## This isn't new Though the premise of their concerns seems reasonable, it's dangerous and an all too common occurrence with the emergence of new technologies. For example, in their example in the podcast, they refer to the technological breakthrough of oil. Oil as energy was a technological marvel and changed the course of human civilization. The embrace of oil — now the cornerstone of industry in our age — revolutionized how societies operated, fueled economies, and connected the world in unprecedented ways. Yet recently, as ideas of its environmental and geopolitical ramifications propagated, the narrative around oil has shifted. Tristan and Aza detail this shift and claim that though the period was great for humanity, we didn't have another technology to go to once the technological consequences became apparent. The problem with that argument is that we did innovate to a better alternative: nuclear. However, at its technological breakthrough, it was met with severe suspicions, from safety concerns to ethical debates over its use. This overregulation due to these concerns caused a decades-long stagnation in nuclear innovation, where even today, we are still stuck with heavy reliance on coal and oil. The scare tactics and fear-mongering had consequences, and, interestingly, they don't see the parallels with their current deceleration stance on AI. These examples underscore a critical insight: the initial anxiety surrounding new technologies is a natural response to the unknowns they introduce. Yet, history shows that too much anxiety can stifle the innovation needed to address the problems posed by current technologies. The cycle of discovery, fear, adaptation, and eventual acceptance reveals an essential truth—progress requires not just the courage to innovate but also the resilience to navigate the uncertainties these innovations bring. Moreover, believing we can predict and plan for all AI-related unknowns reflects overconfidence in our understanding and foresight. History shows that technological progress, marked by unexpected outcomes and discoveries, defies such predictions. The evolution from the printing press to the internet underscores progress's unpredictability. Hence, facing AI's future requires caution, curiosity, and humility. Acknowledging our limitations and embracing continuous learning and adaptation will allow us to harness AI's potential responsibly, illustrating that embracing our uncertainties, rather than pretending to foresee them, is vital to innovation. The journey of technological advancement is fraught with both promise and trepidation. Historically, each significant leap forward, from the dawn of the industrial age to the digital revolution, has been met with a mix of enthusiasm and apprehension. Aza Raskin and Tristan Harris's thesis in the 'AI Dilemma' embodies the latter. ## Who defines "safe?" When slowing down technologies for safety or ethical reasons, the issue arises of who gets to define what "safe" or “ethical” mean? This inquiry is not merely technical but deeply ideological, touching the very core of societal values and power dynamics. For example, the push for Diversity, Equity, and Inclusion (DEI) initiatives shows how specific ideological underpinnings can shape definitions of safety and decency. Take the case of the initial release of Google's AI chatbot, Gemini, which chose the ideology of its creators over truth. Luckily, the answers were so ridiculous that the pushback was sudden and immediate. My worry, however, is if, in correcting this, they become experts in making the ideological capture much more subtle. Large bureaucratic institutions' top-down safety enforcement creates a fertile ground for ideological capture of safety standards.  I claim that the issue is not the technology itself but the lens through which we view and regulate it. Suppose the gatekeepers of 'safety' are aligned with a singular ideology. In that case, AI development would skew to serve specific ends, sidelining diverse perspectives and potentially stifling innovative thought and progress. In the podcast, Tristan and Aza suggest such manipulation as a solution. They propose using AI for consensus-building and creating "shared realities" to address societal challenges. In practice, this means that when individuals' viewpoints seem to be far apart, we can leverage AI to "bridge the gap." How they bridge the gap and what we would bridge it toward is left to the imagination, but to me, it is clear. Regulators will inevitably influence it from the top down, which, in my opinion, would be the opposite of progress. In navigating this terrain, we must advocate for a pluralistic approach to defining safety, encompassing various perspectives and values achieved through market forces rather than a governing entity choosing winners. The more players that can play the game, the more wide-ranging perspectives will catalyze innovation to flourish. ## Ownership & Identity Just because we should accelerate AI forward does not mean I do not have my concerns. When I think about what could be the most devastating for society, I don't believe we have to worry about a Matrix-level dystopia; I worry about freedom. As I explored in "[Whose data is it anyway?](https://cwilbzz.com/whose-data-is-it-anyway/)," my concern gravitates toward the issues of data ownership and the implications of relinquishing control over our digital identities. This relinquishment threatens our privacy and the integrity of the content we generate, leaving it susceptible to the inclinations and profit of a few dominant tech entities. To counteract these concerns, a paradigm shift towards decentralized models of data ownership is imperative. Such standards would empower individuals with control over their digital footprints, ensuring that we develop AI systems with diverse, honest, and truthful perspectives rather than the massaged, narrow viewpoints of their creators. This shift safeguards individual privacy and promotes an ethical framework for AI development that upholds the principles of fairness and impartiality. As we stand at the crossroads of technological innovation and ethical consideration, it is crucial to advocate for systems that place data ownership firmly in the hands of users. By doing so, we can ensure that the future of AI remains truthful, non-ideological, and aligned with the broader interests of society. ## But what about the Matrix? I know I am in the minority on this, but I feel that the concerns of AGI (Artificial General Intelligence) are generally overblown. I am not scared of reaching the point of AGI, and I think the idea that AI will become so intelligent that we will lose control of it is unfounded and silly. Reaching AGI is not reaching consciousness; being worried about it spontaneously gaining consciousness is a misplaced fear. It is a tool created by humans for humans to enhance productivity and achieve specific outcomes. At a technical level, large language models (LLMs) are trained on extensive datasets and learning patterns from language and data through a technique called "unsupervised learning" (meaning the data is untagged). They predict the next word in sentences, refining their predictions through feedback to improve coherence and relevance. When queried, LLMs generate responses based on learned patterns, simulating an understanding of language to provide contextually appropriate answers. They will only answer based on the datasets that were inputted and scanned. AI will never be "alive," meaning that AI lacks inherent agency, consciousness, and the characteristics of life, not capable of independent thought or action. AI cannot act independently of human control. Concerns about AI gaining autonomy and posing a threat to humanity are based on a misunderstanding of the nature of AI and the fundamental differences between living beings and machines. AI spontaneously developing a will or consciousness is more similar to thinking a hammer will start walking than us being able to create consciousness through programming. Right now, there is only one way to create consciousness, and I'm skeptical that is ever something we will be able to harness and create as humans. Irrespective of its complexity — and yes, our tools will continue to become evermore complex — machines, specifically AI, cannot transcend their nature as non-living, inanimate objects programmed and controlled by humans.  The advancement of AI should be seen as enhancing human capabilities, not as a path toward creating autonomous entities with their own wills. So, while AI will continue to evolve, improve, and become more powerful, I believe it will remain under human direction and control without the existential threats often sensationalized in discussions about AI's future. With this framing, we should not view the race toward AGI as something to avoid. This will only make the tools we use more powerful, making us more productive. With all this being said, AGI is still much farther away than many believe. Today's AI excels in specific, narrow tasks, known as narrow or weak AI. These systems operate within tightly defined parameters, achieving remarkable efficiency and accuracy that can sometimes surpass human performance in those specific tasks. Yet, this is far from the versatile and adaptable functionality that AGI represents. Moreover, the exponential growth of computational power observed in the past decades does not directly translate to an equivalent acceleration in achieving AGI. AI's impressive feats are often the result of massive data inputs and computing resources tailored to specific tasks. These successes do not inherently bring us closer to understanding or replicating the general problem-solving capabilities of the human mind, which again would only make the tools more potent in _our_ hands. While AI will undeniably introduce challenges and change the aspects of conflict and power dynamics, these challenges will primarily stem from humans wielding this powerful tool rather than the technology itself. AI is a mirror reflecting our own biases, values, and intentions. The crux of future AI-related issues lies not in the technology's inherent capabilities but in how it is used by those wielding it. This reality is at odds with the idea that we should slow down development as our biggest threat will come from those who are not friendly to us. ## AI Beget's AI While the unknowns of AI development and its pitfalls indeed stir apprehension, it's essential to recognize the power of market forces and human ingenuity in leveraging AI to address these challenges. History is replete with examples of new technologies raising concerns, only for those very technologies to provide solutions to the problems they initially seemed to exacerbate. It looks silly and unfair to think of fighting a war with a country that never embraced oil and was still primarily getting its energy from burning wood.  The evolution of AI is no exception to this pattern. As we venture into uncharted territories, the potential issues that arise with AI—be it ethical concerns, use by malicious actors, biases in decision-making, or privacy intrusions—are not merely obstacles but opportunities for innovation. It is within the realm of possibility, and indeed, probability, that AI will play a crucial role in solving the problems it creates. The idea that there would be no incentive to address and solve these problems is to underestimate the fundamental drivers of technological progress. Market forces, fueled by the demand for better, safer, and more efficient solutions, are powerful catalysts for positive change. When a problem is worth fixing, it invariably attracts the attention of innovators, researchers, and entrepreneurs eager to solve it. This dynamic has driven progress throughout history, and AI is poised to benefit from this problem-solving cycle. Thus, rather than viewing AI's unknowns as sources of fear, we should see them as sparks of opportunity. By tackling the challenges posed by AI, we will harness its full potential to benefit humanity. By fostering an ecosystem that encourages exploration, innovation, and problem-solving, we can ensure that AI serves as a force for good, solving problems as profound as those it might create. This is the optimism we must hold onto—a belief in our collective ability to shape AI into a tool that addresses its own challenges and elevates our capacity to solve some of society's most pressing issues. ## An AI Future The reality is that it isn't whether AI will lead to unforeseen challenges—it undoubtedly will, as has every major technological leap in history. The real issue is whether we let fear dictate our path and confine us to a standstill or embrace AI's potential to address current and future challenges. The approach to solving potential AI-related problems with stringent regulations and a slowdown in innovation is akin to cutting off the nose to spite the face. It's a strategy that risks stagnating the U.S. in a global race where other nations will undoubtedly continue their AI advancements. This perspective dangerously ignores that AI, much like the printing press of the past, has the power to democratize information, empower individuals, and dismantle outdated power structures. The way forward is not less AI but more of it, more innovation, optimism, and curiosity for the remarkable technological breakthroughs that will come. We must recognize that the solution to AI-induced challenges lies not in retreating but in advancing our capabilities to innovate and adapt. AI represents a frontier of limitless possibilities. If wielded with foresight and responsibility, it's a tool that can help solve some of the most pressing issues we face today. There are certainly challenges ahead, but I trust that with problems come solutions. Let's keep the AI Decels from steering us away from this path with their doomsday predictions. Instead, let's embrace AI with the cautious optimism it deserves, forging a future where technology and humanity advance to heights we can't imagine. @ 3c984938:2ec11289
2024-06-09 14:40:55I'm having some pain in my heart about the U.S. elections.  Ever since Obama campaigned for office, an increase of young voters have come out of the woodwork. Things have not improved. They've actively told you that "**your vote matters.**" I believe this to be a lie unless any citizen can demand at the gate, at the White House to be allowed to hold and point a gun to the president's head. (**Relax**, this is a hyperbole) Why so dramatic? Well, what does the president do? Sign bills, commands the military, nominates new Fed chairman, ambassadors, supreme judges and senior officials all while traveling in luxury planes and living in a white palace for four years. They promised **Every TIME** to protect citizen rights when they take the oath and office. *...They've broken this several times, with so-called "emergency-crisis"*  The purpose of a president, today, it seems is to basically hire armed thugs to keep the citizens in check and make sure you "voluntarily continue to be a slave," to the system, hence the IRS. The corruption extends from the cop to the judge and even to politicians. The politicians get paid from lobbyists to create bills in congress for the president to sign. There's no right answer when money is involved with politicians. It is the same if you vote Obama, Biden, Trump, or Haley. They will wield the pen to serve themselves to **say** it will benefit the country. In the first 100 years of presidency, the government wasn't even a big deal. They didn't even interfere with your life as much as they do today.  ^^ You hold the **power** in your hands, don't let them take it. Don't believe me? Try to get a loan from a bank without a signature. Your signature is as good as gold (if not better) and is an original trademark. Just Don't Vote. End the Fed. Opt out.  ^^ I choose to form my own path, even if it means leaving everything I knew prior. It doesn't have to be a spiritual thing. Some, have called me religious because of this. We're all capable of greatness and having humanity. ✨Don't have a machine heart with a machine mind. Instead, choose to have a heart like the cowardly lion from the "**Wizard Of Oz.**" There's no such thing as a good president or politicians. If there was, they would have issued *non-interest* **Federal Reserve Notes.** Lincoln and Kennedy tried to do this, they got shot. There's still a banner of America there, but it's so far gone that I cannot even recognize it. However, I only see a bunch of 🏳🌈 pride flags. ✨Patrick Henry got it wrong, when he delivered his speech, "Give me liberty or give me death." Liberty and freedom are two completely different things. Straightforward from Merriam-Webster Choose Right or left?  No control, to be 100% without restrictions- free.  ✨I disagree with the example sentence given. Because you cannot advocate for human freedom and own slaves, it's contradicting it. Which was common in the founding days. I can understand many may disagree with me, and you might be thinking, "**This time will be different.**" I, respectfully, disagree, and the proxy wars are proof. Learn the importance of Bitcoin, every **Satoshi** is a step away from corruption. ✨What does it look like to pull the curtains from the "**Wizard of Oz?**" 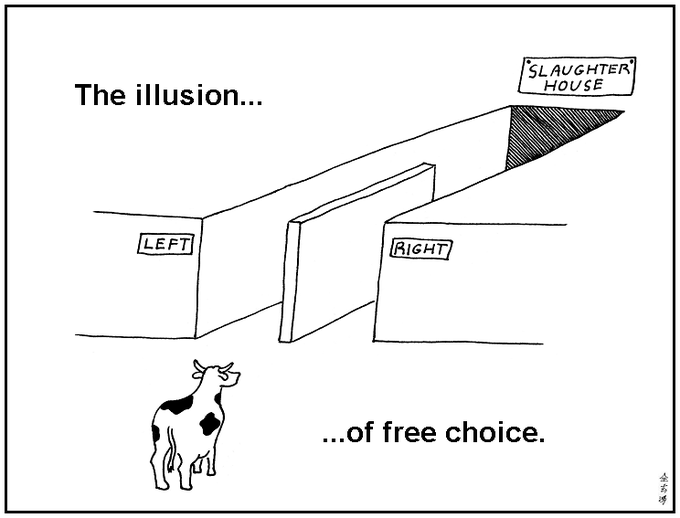 Have you watched the video below, what 30 Trillion dollars in debt looks like visually? Even I was blown away. https://video.nostr.build/d58c5e1afba6d7a905a39407f5e695a4eb4a88ae692817a36ecfa6ca1b62ea15.mp4  I say this with love. Hear my plea? Normally, I don't write about anything political. It just feels like a losing game. My energy feels it's in better use to learn new things, write and to create. Even a simple blog post as simple as this. Stack SATs, and stay humble. <3 Onigirl
@ 3c984938:2ec11289
2024-06-09 14:40:55I'm having some pain in my heart about the U.S. elections.  Ever since Obama campaigned for office, an increase of young voters have come out of the woodwork. Things have not improved. They've actively told you that "**your vote matters.**" I believe this to be a lie unless any citizen can demand at the gate, at the White House to be allowed to hold and point a gun to the president's head. (**Relax**, this is a hyperbole) Why so dramatic? Well, what does the president do? Sign bills, commands the military, nominates new Fed chairman, ambassadors, supreme judges and senior officials all while traveling in luxury planes and living in a white palace for four years. They promised **Every TIME** to protect citizen rights when they take the oath and office. *...They've broken this several times, with so-called "emergency-crisis"*  The purpose of a president, today, it seems is to basically hire armed thugs to keep the citizens in check and make sure you "voluntarily continue to be a slave," to the system, hence the IRS. The corruption extends from the cop to the judge and even to politicians. The politicians get paid from lobbyists to create bills in congress for the president to sign. There's no right answer when money is involved with politicians. It is the same if you vote Obama, Biden, Trump, or Haley. They will wield the pen to serve themselves to **say** it will benefit the country. In the first 100 years of presidency, the government wasn't even a big deal. They didn't even interfere with your life as much as they do today.  ^^ You hold the **power** in your hands, don't let them take it. Don't believe me? Try to get a loan from a bank without a signature. Your signature is as good as gold (if not better) and is an original trademark. Just Don't Vote. End the Fed. Opt out.  ^^ I choose to form my own path, even if it means leaving everything I knew prior. It doesn't have to be a spiritual thing. Some, have called me religious because of this. We're all capable of greatness and having humanity. ✨Don't have a machine heart with a machine mind. Instead, choose to have a heart like the cowardly lion from the "**Wizard Of Oz.**" There's no such thing as a good president or politicians. If there was, they would have issued *non-interest* **Federal Reserve Notes.** Lincoln and Kennedy tried to do this, they got shot. There's still a banner of America there, but it's so far gone that I cannot even recognize it. However, I only see a bunch of 🏳🌈 pride flags. ✨Patrick Henry got it wrong, when he delivered his speech, "Give me liberty or give me death." Liberty and freedom are two completely different things. Straightforward from Merriam-Webster Choose Right or left?  No control, to be 100% without restrictions- free.  ✨I disagree with the example sentence given. Because you cannot advocate for human freedom and own slaves, it's contradicting it. Which was common in the founding days. I can understand many may disagree with me, and you might be thinking, "**This time will be different.**" I, respectfully, disagree, and the proxy wars are proof. Learn the importance of Bitcoin, every **Satoshi** is a step away from corruption. ✨What does it look like to pull the curtains from the "**Wizard of Oz?**" 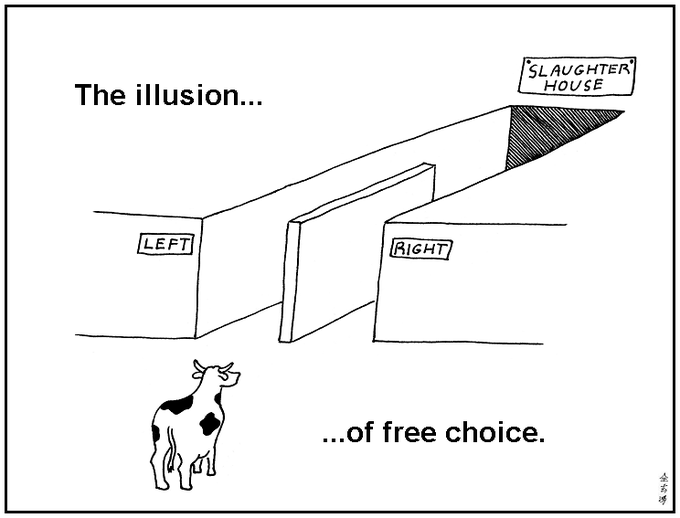 Have you watched the video below, what 30 Trillion dollars in debt looks like visually? Even I was blown away. https://video.nostr.build/d58c5e1afba6d7a905a39407f5e695a4eb4a88ae692817a36ecfa6ca1b62ea15.mp4  I say this with love. Hear my plea? Normally, I don't write about anything political. It just feels like a losing game. My energy feels it's in better use to learn new things, write and to create. Even a simple blog post as simple as this. Stack SATs, and stay humble. <3 Onigirl @ 3bf0c63f:aefa459d
2024-05-21 12:38:08# Bitcoin transactions explained A transaction is a piece of data that takes **inputs** and produces **outputs**. Forget about the blockchain thing, Bitcoin is actually just a big tree of transactions. The blockchain is just a way to keep transactions ordered. Imagine you have 10 satoshis. That means you have them in an unspent transaction output (**UTXO**). You want to spend them, so you create a transaction. The transaction should reference unspent outputs as its inputs. Every transaction has an immutable id, so you use that id plus the index of the output (because transactions can have multiple outputs). Then you specify a **script** that unlocks that transaction and related signatures, then you specify outputs along with a **script** that locks these outputs.  As you can see, there's this lock/unlocking thing and there are inputs and outputs. Inputs must be unlocked by fulfilling the conditions specified by the person who created the transaction they're in. And outputs must be locked so anyone wanting to spend those outputs will need to unlock them. For most of the cases locking and unlocking means specifying a **public key** whose controller (the person who has the corresponding **private key**) will be able to spend. Other fancy things are possible too, but we can ignore them for now. Back to the 10 satoshis you want to spend. Since you've successfully referenced 10 satoshis and unlocked them, now you can specify the outputs (this is all done in a single step). You can specify one output of 10 satoshis, two of 5, one of 3 and one of 7, three of 3 and so on. The sum of outputs can't be more than 10. And if the sum of outputs is less than 10 the difference goes to fees. In the first days of Bitcoin you didn't need any fees, but now you do, otherwise your transaction won't be included in any block.  If you're still interested in transactions maybe you could take a look at [this small chapter](https://github.com/bitcoinbook/bitcoinbook/blob/6d1c26e1640ae32b28389d5ae4caf1214c2be7db/ch06_transactions.adoc) of that Andreas Antonopoulos book. If you hate Andreas Antonopoulos because he is a communist shitcoiner or don't want to read more than half a page, go here: <https://en.bitcoin.it/wiki/Coin_analogy>
@ 3bf0c63f:aefa459d
2024-05-21 12:38:08# Bitcoin transactions explained A transaction is a piece of data that takes **inputs** and produces **outputs**. Forget about the blockchain thing, Bitcoin is actually just a big tree of transactions. The blockchain is just a way to keep transactions ordered. Imagine you have 10 satoshis. That means you have them in an unspent transaction output (**UTXO**). You want to spend them, so you create a transaction. The transaction should reference unspent outputs as its inputs. Every transaction has an immutable id, so you use that id plus the index of the output (because transactions can have multiple outputs). Then you specify a **script** that unlocks that transaction and related signatures, then you specify outputs along with a **script** that locks these outputs.  As you can see, there's this lock/unlocking thing and there are inputs and outputs. Inputs must be unlocked by fulfilling the conditions specified by the person who created the transaction they're in. And outputs must be locked so anyone wanting to spend those outputs will need to unlock them. For most of the cases locking and unlocking means specifying a **public key** whose controller (the person who has the corresponding **private key**) will be able to spend. Other fancy things are possible too, but we can ignore them for now. Back to the 10 satoshis you want to spend. Since you've successfully referenced 10 satoshis and unlocked them, now you can specify the outputs (this is all done in a single step). You can specify one output of 10 satoshis, two of 5, one of 3 and one of 7, three of 3 and so on. The sum of outputs can't be more than 10. And if the sum of outputs is less than 10 the difference goes to fees. In the first days of Bitcoin you didn't need any fees, but now you do, otherwise your transaction won't be included in any block.  If you're still interested in transactions maybe you could take a look at [this small chapter](https://github.com/bitcoinbook/bitcoinbook/blob/6d1c26e1640ae32b28389d5ae4caf1214c2be7db/ch06_transactions.adoc) of that Andreas Antonopoulos book. If you hate Andreas Antonopoulos because he is a communist shitcoiner or don't want to read more than half a page, go here: <https://en.bitcoin.it/wiki/Coin_analogy> @ 3c984938:2ec11289
2024-05-09 04:43:15 It's been a journey from the Publishing Forest of Nostr to the open sea of web3. I've come across a beautiful chain of islands and thought. Why not take a break and explore this place? If I'm searching for devs and FOSS, I should search every nook and cranny inside the realm of Nostr. It is quite vast for little old me. I'm just a little hamster and I don't speak in code or binary numbers zeros and ones.  After being in sea for awhile, my heart raced for excitement for what I could find. It seems I wasn't alone, there were others here like me! Let's help spread the message to others about this uncharted realm. See, look at the other sailboats, aren't they pretty? Thanks to some generous donation of SATs, I was able to afford the docking fee.  Ever feel like everyone was going to a party, and you were supposed to dress up, but you missed the memo? Or a comic-con? well, I felt completely underdressed and that's an understatement. Well, turns out there is a some knights around here. Take a peek!  A black cat with a knight passed by very quickly. He was moving too fast for me to track. Where was he going? Then I spotted a group of knights heading in the same direction, so I tagged along. The vibes from these guys was impossible to resist. They were just happy-go-lucky. 🥰They were heading to a tavern on a cliff off the island.  Ehh? a Tavern? Slightly confused, whatever could these knights be doing here? I guess when they're done with their rounds they would here to blow off steam. Things are looking curiouser and curiouser. But the black cat from earlier was here with its rider, whom was dismounting. So you can only guess, where I'm going.  The atmosphere in this pub, was lively and energetic. So many knights spoke among themselves. A group here, another there, but there was one that caught my eye. I went up to a group at a table, whose height towed well above me even when seated. Taking a deep breath, I asked, "Who manages this place?" They unanimous pointed to one waiting for ale at the bar. What was he doing? Watching others talk? How peculiar.  So I went up to him! And introduced myself. >"Hello I'm Onigirl" >>"Hello Onigirl, Welcome to Gossip" >>>"Gossip, what is Gossip?" scratching my head and whiskers. What is Gossip? Gossip is FOSS and a great client for **privacy-centric minded nostriches**. It avoids browser tech which by-passes several scripting languages such as JavaScript☕, HTML parsing, rendering, and CSS(Except HTTP GET and Websockets). Using OpenGL-style rendering. **For Nostriches that wish to remain anonymous can use Gossip over TOR.** Mike recommends using QubesOS, Whonix and or Tails. [FYI-Gossip does not natively support tor SOCKS5 proxy] Most helpful to spill the beans if you're a journalist.  On top of using your nsec or your encryption key, Gossip adds another layer of security over your account with a password login. There's nothing wrong with using the browser extensions (such as nos2x or Flamingo) which makes it super easy to log in to Nostr enable websites, apps, but it does expose you to browser vulnerabilities. Mike Points out >"people have already had their private key stolen from other nostr clients," so it a concern if you value your account. I most certainly care for mine.  Gossip UI has a simple, and clean interface revolving around NIP-65 also called the “Outbox model." As posted from [GitHub](https://github.com/nostr-protocol/nips/blob/master/65.md), >"This NIP allows Clients to connect directly with the most up-to-date relay set from each individual user, eliminating the need of broadcasting events to popular relays." This eliminates clients that track only a specific set of relays which can congest those relays when you publish your note. Also this can be censored, by using Gossip you can publish notes to alternative relays that have not censored you to reach the same followers. 👉The easiest way to translate that is reducing redundancy to publish to popular relays or centralized relays for content reach to your followers.  Cool! What an awesome client, I mean Tavern! What else does this knight do? He reaches for something in his pocket. what is it? A Pocket is a database for storing and retrieving nostr events but mike's written it in Rust with a few extra kinks inspired by Will's nostrdb. Still in development, but it'll be another tool for you dear user! 💖💕💚 Onigirl is proud to present this knights to the community and honor them with kisu. 💋💋💋 Show some 💖💘💓🧡💙💚 👉💋💋Will - jb55 Lord of apples 💋 @npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s 👉💋💋 Mike Knight - Lord of Security 💋 @npub1acg6thl5psv62405rljzkj8spesceyfz2c32udakc2ak0dmvfeyse9p35c  Knights spend a lot of time behind the screen coding for the better of humanity. It is a tough job! Let's appreciate these knights, relay operators, that support this amazing realm of Nostr! FOSS for all!  This article was prompted for the need for privacy and security of your data. They're different, not to be confused. Recently, Edward Snowden warns Bitcoin devs about the need for privacy, [Quote](https://twitter.com/Snowden/status/1786170805728039127): >“I've been warning Bitcoin developers for ten years that privacy needs to be provided for at the protocol level. This is the final warning. The clock is ticking.” Snowden’s comments come after heavy actions of enforcement from Samarai Wallet, Roger Ver, Binance’s CZ, and now the closure of Wasabi Wallet. Additionally, according to [CryptoBriefing](https://cryptobriefing.com/trezor-coinjoin-shutdown/), Trezor is ending it’s CoinJoin integration as well. Many are concerned over the new definition of a money transmitter, which includes even those who don’t touch the funds. ### Help your favorite the hamster  ^^Me drowning in notes on your feed. I can only eat so many notes to find you. 👉If there are any XMPP fans on here. I'm open to the idea of opening a public channel, so you could follow me on that as a *forum-like style*. My server of choice would likely be a German server.😀You would be receiving my articles as njump.me style or website-like. GrapeneOS users, you can download Cheogram app from the F-Driod store for free to access. Apple and Andriod users are subjected to pay to download this app, an alternative is **ntalk or conversations**. *If it interests the community, just FYI. Please comment or DM.* 👉If you enjoyed this content, please consider **reposting/sharing** as *my content is easily drowned by notes* on your feed. You could also *join my community under Children_Zone where I post my content.* An alternative is by following #onigirl Just FYI this feature is currently a little buggy. Follow as I search for tools and awesome devs to help you dear user live a decentralized life as I explore the realm of Nostr. Thank you Fren
@ 3c984938:2ec11289
2024-05-09 04:43:15 It's been a journey from the Publishing Forest of Nostr to the open sea of web3. I've come across a beautiful chain of islands and thought. Why not take a break and explore this place? If I'm searching for devs and FOSS, I should search every nook and cranny inside the realm of Nostr. It is quite vast for little old me. I'm just a little hamster and I don't speak in code or binary numbers zeros and ones.  After being in sea for awhile, my heart raced for excitement for what I could find. It seems I wasn't alone, there were others here like me! Let's help spread the message to others about this uncharted realm. See, look at the other sailboats, aren't they pretty? Thanks to some generous donation of SATs, I was able to afford the docking fee.  Ever feel like everyone was going to a party, and you were supposed to dress up, but you missed the memo? Or a comic-con? well, I felt completely underdressed and that's an understatement. Well, turns out there is a some knights around here. Take a peek!  A black cat with a knight passed by very quickly. He was moving too fast for me to track. Where was he going? Then I spotted a group of knights heading in the same direction, so I tagged along. The vibes from these guys was impossible to resist. They were just happy-go-lucky. 🥰They were heading to a tavern on a cliff off the island.  Ehh? a Tavern? Slightly confused, whatever could these knights be doing here? I guess when they're done with their rounds they would here to blow off steam. Things are looking curiouser and curiouser. But the black cat from earlier was here with its rider, whom was dismounting. So you can only guess, where I'm going.  The atmosphere in this pub, was lively and energetic. So many knights spoke among themselves. A group here, another there, but there was one that caught my eye. I went up to a group at a table, whose height towed well above me even when seated. Taking a deep breath, I asked, "Who manages this place?" They unanimous pointed to one waiting for ale at the bar. What was he doing? Watching others talk? How peculiar.  So I went up to him! And introduced myself. >"Hello I'm Onigirl" >>"Hello Onigirl, Welcome to Gossip" >>>"Gossip, what is Gossip?" scratching my head and whiskers. What is Gossip? Gossip is FOSS and a great client for **privacy-centric minded nostriches**. It avoids browser tech which by-passes several scripting languages such as JavaScript☕, HTML parsing, rendering, and CSS(Except HTTP GET and Websockets). Using OpenGL-style rendering. **For Nostriches that wish to remain anonymous can use Gossip over TOR.** Mike recommends using QubesOS, Whonix and or Tails. [FYI-Gossip does not natively support tor SOCKS5 proxy] Most helpful to spill the beans if you're a journalist.  On top of using your nsec or your encryption key, Gossip adds another layer of security over your account with a password login. There's nothing wrong with using the browser extensions (such as nos2x or Flamingo) which makes it super easy to log in to Nostr enable websites, apps, but it does expose you to browser vulnerabilities. Mike Points out >"people have already had their private key stolen from other nostr clients," so it a concern if you value your account. I most certainly care for mine.  Gossip UI has a simple, and clean interface revolving around NIP-65 also called the “Outbox model." As posted from [GitHub](https://github.com/nostr-protocol/nips/blob/master/65.md), >"This NIP allows Clients to connect directly with the most up-to-date relay set from each individual user, eliminating the need of broadcasting events to popular relays." This eliminates clients that track only a specific set of relays which can congest those relays when you publish your note. Also this can be censored, by using Gossip you can publish notes to alternative relays that have not censored you to reach the same followers. 👉The easiest way to translate that is reducing redundancy to publish to popular relays or centralized relays for content reach to your followers.  Cool! What an awesome client, I mean Tavern! What else does this knight do? He reaches for something in his pocket. what is it? A Pocket is a database for storing and retrieving nostr events but mike's written it in Rust with a few extra kinks inspired by Will's nostrdb. Still in development, but it'll be another tool for you dear user! 💖💕💚 Onigirl is proud to present this knights to the community and honor them with kisu. 💋💋💋 Show some 💖💘💓🧡💙💚 👉💋💋Will - jb55 Lord of apples 💋 @npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s 👉💋💋 Mike Knight - Lord of Security 💋 @npub1acg6thl5psv62405rljzkj8spesceyfz2c32udakc2ak0dmvfeyse9p35c  Knights spend a lot of time behind the screen coding for the better of humanity. It is a tough job! Let's appreciate these knights, relay operators, that support this amazing realm of Nostr! FOSS for all!  This article was prompted for the need for privacy and security of your data. They're different, not to be confused. Recently, Edward Snowden warns Bitcoin devs about the need for privacy, [Quote](https://twitter.com/Snowden/status/1786170805728039127): >“I've been warning Bitcoin developers for ten years that privacy needs to be provided for at the protocol level. This is the final warning. The clock is ticking.” Snowden’s comments come after heavy actions of enforcement from Samarai Wallet, Roger Ver, Binance’s CZ, and now the closure of Wasabi Wallet. Additionally, according to [CryptoBriefing](https://cryptobriefing.com/trezor-coinjoin-shutdown/), Trezor is ending it’s CoinJoin integration as well. Many are concerned over the new definition of a money transmitter, which includes even those who don’t touch the funds. ### Help your favorite the hamster  ^^Me drowning in notes on your feed. I can only eat so many notes to find you. 👉If there are any XMPP fans on here. I'm open to the idea of opening a public channel, so you could follow me on that as a *forum-like style*. My server of choice would likely be a German server.😀You would be receiving my articles as njump.me style or website-like. GrapeneOS users, you can download Cheogram app from the F-Driod store for free to access. Apple and Andriod users are subjected to pay to download this app, an alternative is **ntalk or conversations**. *If it interests the community, just FYI. Please comment or DM.* 👉If you enjoyed this content, please consider **reposting/sharing** as *my content is easily drowned by notes* on your feed. You could also *join my community under Children_Zone where I post my content.* An alternative is by following #onigirl Just FYI this feature is currently a little buggy. Follow as I search for tools and awesome devs to help you dear user live a decentralized life as I explore the realm of Nostr. Thank you Fren @ 266815e0:6cd408a5
2024-04-24 23:02:21> NOTE: this is just a quick technical guide. sorry for the lack of details ## Install NodeJS Download it from the official website https://nodejs.org/en/download Or use nvm https://github.com/nvm-sh/nvm?tab=readme-ov-file#install--update-script ```bash wget -qO- https://raw.githubusercontent.com/nvm-sh/nvm/v0.39.7/install.sh | bash nvm install 20 ``` ## Clone example config.yml ```bash wget https://raw.githubusercontent.com/hzrd149/blossom-server/master/config.example.yml -O config.yml ``` ## Modify config.yml ```bash nano config.yml # or if your that type of person vim config.yml ``` ## Run blossom-server ```bash npx blossom-server-ts # or install it locally and run using npm npm install blossom-server-ts ./node_modules/.bin/blossom-server-ts ``` Now you can open http://localhost:3000 and see your blossom server And if you set the `dashboard.enabled` option in the `config.yml` you can open http://localhost:3000/admin to see the admin dashboard
@ 266815e0:6cd408a5
2024-04-24 23:02:21> NOTE: this is just a quick technical guide. sorry for the lack of details ## Install NodeJS Download it from the official website https://nodejs.org/en/download Or use nvm https://github.com/nvm-sh/nvm?tab=readme-ov-file#install--update-script ```bash wget -qO- https://raw.githubusercontent.com/nvm-sh/nvm/v0.39.7/install.sh | bash nvm install 20 ``` ## Clone example config.yml ```bash wget https://raw.githubusercontent.com/hzrd149/blossom-server/master/config.example.yml -O config.yml ``` ## Modify config.yml ```bash nano config.yml # or if your that type of person vim config.yml ``` ## Run blossom-server ```bash npx blossom-server-ts # or install it locally and run using npm npm install blossom-server-ts ./node_modules/.bin/blossom-server-ts ``` Now you can open http://localhost:3000 and see your blossom server And if you set the `dashboard.enabled` option in the `config.yml` you can open http://localhost:3000/admin to see the admin dashboard @ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS There were a few things I learned from all these conversations: 1. All the existing solutions have one thing in common. A universal ID of some kind for files 2. HTTP is still good. we don't have to throw the baby out with the bath water 3. nostr could fix this... somehow Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing... ## An Identity system An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends) ## What is blossom? Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id ## What are Blobs? blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names Instead blobs have a sha256 hash (like `b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553`) as an ID These IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using: `sha256sum bitcoin.pdf` ) ## How do the servers work? Blossom servers expose four endpoints to let clients and users upload and manage blobs - `GET /<sha256>` (optional file `.ext`) - `PUT /upload` - `Authentication`: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#upload-authorization-required) - Returns a blob descriptor - `GET /list/<pubkey>` - Returns an array of blob descriptors - `Authentication` _(optional)_: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#list-authorization-optional) - `DELETE /<sha256>` - `Authentication`: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#delete-authorization-required) ## What is Blossom Drive? Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs ## What are Drives Drives are just nostr events (kind `30563`) that store a map of blobs and what filename they should have along with some extra metadata An example drive event would be ```json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] } ``` There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at If your interested, the full event definition is at [github.com/hzrd149/blossom-drive](https://github.com/hzrd149/blossom-drive/blob/master/docs/drive.md) ## Getting started Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started ### 1. Open the app Open https://blossom.hzrd149.com ### 2. Login using extension  You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an `ncryptsec` password protected private key - a `nsec` unprotected private key (please don't) - bunker:// URI from nsecbunker ### 3. Add a blossom server  Right now `https://cdn.satellite.earth` is the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript [github.com/hzrd149/blossom-server](https://github.com/hzrd149/blossom-server) ### 4. Start uploading your files **NOTE: All files upload to blossom drive are public by default. DO NOT upload private files**  ### 5. Manage files  ## Encrypted drives There is also the option to encrypt drives using [NIP-49](https://github.com/nostr-protocol/nips/blob/master/49.md) password encryption. although its not tested at all so don't trust it, verify  ## Whats next? I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything also all the images in this article are stored in one of my blossom drives [here](nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka) nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
@ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS There were a few things I learned from all these conversations: 1. All the existing solutions have one thing in common. A universal ID of some kind for files 2. HTTP is still good. we don't have to throw the baby out with the bath water 3. nostr could fix this... somehow Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing... ## An Identity system An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends) ## What is blossom? Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id ## What are Blobs? blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names Instead blobs have a sha256 hash (like `b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553`) as an ID These IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using: `sha256sum bitcoin.pdf` ) ## How do the servers work? Blossom servers expose four endpoints to let clients and users upload and manage blobs - `GET /<sha256>` (optional file `.ext`) - `PUT /upload` - `Authentication`: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#upload-authorization-required) - Returns a blob descriptor - `GET /list/<pubkey>` - Returns an array of blob descriptors - `Authentication` _(optional)_: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#list-authorization-optional) - `DELETE /<sha256>` - `Authentication`: Signed [nostr event](https://github.com/hzrd149/blossom/blob/master/Server.md#delete-authorization-required) ## What is Blossom Drive? Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs ## What are Drives Drives are just nostr events (kind `30563`) that store a map of blobs and what filename they should have along with some extra metadata An example drive event would be ```json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] } ``` There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at If your interested, the full event definition is at [github.com/hzrd149/blossom-drive](https://github.com/hzrd149/blossom-drive/blob/master/docs/drive.md) ## Getting started Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started ### 1. Open the app Open https://blossom.hzrd149.com ### 2. Login using extension  You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an `ncryptsec` password protected private key - a `nsec` unprotected private key (please don't) - bunker:// URI from nsecbunker ### 3. Add a blossom server  Right now `https://cdn.satellite.earth` is the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript [github.com/hzrd149/blossom-server](https://github.com/hzrd149/blossom-server) ### 4. Start uploading your files **NOTE: All files upload to blossom drive are public by default. DO NOT upload private files**  ### 5. Manage files  ## Encrypted drives There is also the option to encrypt drives using [NIP-49](https://github.com/nostr-protocol/nips/blob/master/49.md) password encryption. although its not tested at all so don't trust it, verify  ## Whats next? I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything also all the images in this article are stored in one of my blossom drives [here](nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka) nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka @ 362ebffa:492e2719
2024-04-20 15:52:12Julian Assange (founder of WikiLeaks) released classified documents in 2010, including sensitive U.S. military and diplomatic information. He faced charges of conspiracy and espionage for his role in obtaining and disseminating the documents. Edward Snowden, (former NSA contractor) leaked classified information in 2013, exposing global surveillance programs. Snowden revealed widespread data collection by intelligence agencies, leading to charges of espionage and theft of government property. As of today in 2024, both Assange and Snowden are considered whistle blowers by some but face legal consequences for their actions, igniting debates on government transparency and individual rights. In a sane democratic World, they should be free! Their efforts to expose government surveillance and misconduct was brave and should be encouraged. But instead they have also faced legal consequences for their actions, with the U.S. government seeking their extradition to face trial on criminal charges. These cases have sparked debates about government transparency, freedom of the press, national security, and the balance between individual rights and state interests. Without whistle blowers, government are becoming bullies!
@ 362ebffa:492e2719
2024-04-20 15:52:12Julian Assange (founder of WikiLeaks) released classified documents in 2010, including sensitive U.S. military and diplomatic information. He faced charges of conspiracy and espionage for his role in obtaining and disseminating the documents. Edward Snowden, (former NSA contractor) leaked classified information in 2013, exposing global surveillance programs. Snowden revealed widespread data collection by intelligence agencies, leading to charges of espionage and theft of government property. As of today in 2024, both Assange and Snowden are considered whistle blowers by some but face legal consequences for their actions, igniting debates on government transparency and individual rights. In a sane democratic World, they should be free! Their efforts to expose government surveillance and misconduct was brave and should be encouraged. But instead they have also faced legal consequences for their actions, with the U.S. government seeking their extradition to face trial on criminal charges. These cases have sparked debates about government transparency, freedom of the press, national security, and the balance between individual rights and state interests. Without whistle blowers, government are becoming bullies! @ 3c984938:2ec11289
2024-04-16 17:14:58## Hello (N)osytrs!  ### Yes! I'm calling you an (N)oystr!  Why is that? Because you shine, and I'm not just saying that to get more SATs. Ordinary Oysters and mussels can produce these beauties! Nothing seriously unique about them, however, with a little time and love each oyster is capable of creating something truly beautiful. I like believing so, at least, given the fact that you're even reading this article; makes you an (N)oystr! This isn't published this on X (formerly known as Twitter), Facebook, Discord, Telegram, or Instagram, which makes you the rare breed! A pearl indeed! I do have access to those platforms, but why create content on a terrible platform knowing I too could be shut down! Unfortunately, many people still use these platforms. This forces individuals to give up their privacy every day. Meta is leading the charge by forcing users to provide a photo ID for verification in order to use their crappy, obsolete site. If that was not bad enough, imagine if you're having a type of disagreement or opinion. Then, Bigtech can easily deplatform you. Umm. So no open debate? Just instantly shut-off users. Whatever, happened to right to a fair trial? Nope, just burning you at the stake as if you're a witch or warlock!  How heinous are the perpetrators and financiers of this? Well, that's opening another can of worms for you. Imagine your voice being taken away, like the little mermaid. Ariel was lucky to have a prince, but the majority of us? The likelihood that I would be carried away by the current of the sea during a sunset with a prince on a sailboat is zero. And I live on an island, so I'm just missing the prince, sailboat(though I know where I could go to steal one), and red hair. Oh my gosh, now I feel sad.  I do not have the prince, Bob is better! I do not have mermaid fins, or a shell bra. Use coconut shells, it offers more support! But, I still have my voice and a killer sunset to die for! All of that is possible thanks to the work of developers. These knights fight for Freedom Tech by utilizing FOSS, which help provides us with a vibrant ecosystem. Unfortunately, I recently learned that **they are not all *funded***. Knights must eat, drink, and have a work space. This space is where they spend most of their sweat equity on an app or software that may and may not pan out. That brilliance is susceptible to fading, as these individuals are not seen but rather stay behind closed doors. What's worse, if these developers lose faith in their project and decide to join forces with Meta! 😖 Does WhatsApp ring a bell? Without them, I probably wouldn't be able to create this long form article. Let's cheer them on like cheerleaders.. 👉Unfortunately, there's no cheerleader emoji so you'll just have to settle for a dancing lady, n guy. 💃🕺 Semisol said it beautifully, npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj > If we want freedom tech to succeed, the tools that make it possible need to be funded: relays like https://nostr.land, media hosts like https://nostr.build, clients like https://damus.io, etc. With that thought, Onigirl is pleased to announce the launch of a new series. With a sole focus on free market devs/projects. # Knights of Nostr!  I'll happily brief you about their exciting project and how it benefits humanity! Let's Support these Magnificent projects, devs, relays, and builders! Our first runner up! Oppa Fishcake :Lord of Media Hosting npub137c5pd8gmhhe0njtsgwjgunc5xjr2vmzvglkgqs5sjeh972gqqxqjak37w Oppa Fishcake with his noble steed!  Think of this as an introduction to learn and further your experience on Nostr! New developments and applications are constantly happening on Nostr. It's enough to make one's head spin. I may also cover FOSS projects(outside of Nostr) as they need some love as well! Plus, you can think of it as another tool to add to your decentralized life. I will not be doing how-to-Nostr guides. I personally feel there are plenty of great guides already available! Which I'm happy to add to curation collection via easily searchable on Yakihonne. For email updates you can subscribe to my [[https://paragraph.xyz/@onigirl]] If you like it, send me some 🧡💛💚 hearts💜💗💖 otherwise zap dat⚡⚡🍑🍑peach⚡⚡🍑 ~If not me, then at least to our dearest knight! Thank you from the bottom of my heart for your time and support (N)oystr! Shine bright like a diamond! Share if you care! FOSS power! Follow on your favorite Nostr Client for the best viewing experience! [!NOTE] > I'm using Obsidian + Nostr Writer Plugin; a new way to publish Markdown directly to Nostr. > I was a little nervous using this because I was used doing them in RStudio; R Markdown. > Since this is my first article, I sent it to my account as a draft to test it. It's pretty neat.
@ 3c984938:2ec11289
2024-04-16 17:14:58## Hello (N)osytrs!  ### Yes! I'm calling you an (N)oystr!  Why is that? Because you shine, and I'm not just saying that to get more SATs. Ordinary Oysters and mussels can produce these beauties! Nothing seriously unique about them, however, with a little time and love each oyster is capable of creating something truly beautiful. I like believing so, at least, given the fact that you're even reading this article; makes you an (N)oystr! This isn't published this on X (formerly known as Twitter), Facebook, Discord, Telegram, or Instagram, which makes you the rare breed! A pearl indeed! I do have access to those platforms, but why create content on a terrible platform knowing I too could be shut down! Unfortunately, many people still use these platforms. This forces individuals to give up their privacy every day. Meta is leading the charge by forcing users to provide a photo ID for verification in order to use their crappy, obsolete site. If that was not bad enough, imagine if you're having a type of disagreement or opinion. Then, Bigtech can easily deplatform you. Umm. So no open debate? Just instantly shut-off users. Whatever, happened to right to a fair trial? Nope, just burning you at the stake as if you're a witch or warlock!  How heinous are the perpetrators and financiers of this? Well, that's opening another can of worms for you. Imagine your voice being taken away, like the little mermaid. Ariel was lucky to have a prince, but the majority of us? The likelihood that I would be carried away by the current of the sea during a sunset with a prince on a sailboat is zero. And I live on an island, so I'm just missing the prince, sailboat(though I know where I could go to steal one), and red hair. Oh my gosh, now I feel sad.  I do not have the prince, Bob is better! I do not have mermaid fins, or a shell bra. Use coconut shells, it offers more support! But, I still have my voice and a killer sunset to die for! All of that is possible thanks to the work of developers. These knights fight for Freedom Tech by utilizing FOSS, which help provides us with a vibrant ecosystem. Unfortunately, I recently learned that **they are not all *funded***. Knights must eat, drink, and have a work space. This space is where they spend most of their sweat equity on an app or software that may and may not pan out. That brilliance is susceptible to fading, as these individuals are not seen but rather stay behind closed doors. What's worse, if these developers lose faith in their project and decide to join forces with Meta! 😖 Does WhatsApp ring a bell? Without them, I probably wouldn't be able to create this long form article. Let's cheer them on like cheerleaders.. 👉Unfortunately, there's no cheerleader emoji so you'll just have to settle for a dancing lady, n guy. 💃🕺 Semisol said it beautifully, npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj > If we want freedom tech to succeed, the tools that make it possible need to be funded: relays like https://nostr.land, media hosts like https://nostr.build, clients like https://damus.io, etc. With that thought, Onigirl is pleased to announce the launch of a new series. With a sole focus on free market devs/projects. # Knights of Nostr!  I'll happily brief you about their exciting project and how it benefits humanity! Let's Support these Magnificent projects, devs, relays, and builders! Our first runner up! Oppa Fishcake :Lord of Media Hosting npub137c5pd8gmhhe0njtsgwjgunc5xjr2vmzvglkgqs5sjeh972gqqxqjak37w Oppa Fishcake with his noble steed!  Think of this as an introduction to learn and further your experience on Nostr! New developments and applications are constantly happening on Nostr. It's enough to make one's head spin. I may also cover FOSS projects(outside of Nostr) as they need some love as well! Plus, you can think of it as another tool to add to your decentralized life. I will not be doing how-to-Nostr guides. I personally feel there are plenty of great guides already available! Which I'm happy to add to curation collection via easily searchable on Yakihonne. For email updates you can subscribe to my [[https://paragraph.xyz/@onigirl]] If you like it, send me some 🧡💛💚 hearts💜💗💖 otherwise zap dat⚡⚡🍑🍑peach⚡⚡🍑 ~If not me, then at least to our dearest knight! Thank you from the bottom of my heart for your time and support (N)oystr! Shine bright like a diamond! Share if you care! FOSS power! Follow on your favorite Nostr Client for the best viewing experience! [!NOTE] > I'm using Obsidian + Nostr Writer Plugin; a new way to publish Markdown directly to Nostr. > I was a little nervous using this because I was used doing them in RStudio; R Markdown. > Since this is my first article, I sent it to my account as a draft to test it. It's pretty neat. @ c7eda660:efd97c86
2024-04-14 02:02:19This is a test of Nostr Writer, publishing from Obsidian.
@ c7eda660:efd97c86
2024-04-14 02:02:19This is a test of Nostr Writer, publishing from Obsidian. @ 47750177:8969e41a
2024-04-08 12:00:0025.2 Release Notes ================== Bitcoin Core version 25.2 is now available from: <https://bitcoincore.org/bin/bitcoin-core-25.2> This release includes various bug fixes and performance improvements, as well as updated translations. Please report bugs using the issue tracker at GitHub: <https://github.com/bitcoin/bitcoin/issues> To receive security and update notifications, please subscribe to: <https://bitcoincore.org/en/list/announcements/join/> How to Upgrade ============== If you are running an older version, shut it down. Wait until it has completely shut down (which might take a few minutes in some cases), then run the installer (on Windows) or just copy over `/Applications/Bitcoin-Qt` (on macOS) or `bitcoind`/`bitcoin-qt` (on Linux). Upgrading directly from a version of Bitcoin Core that has reached its EOL is possible, but it might take some time if the data directory needs to be migrated. Old wallet versions of Bitcoin Core are generally supported. Compatibility ============== Bitcoin Core is supported and extensively tested on operating systems using the Linux kernel, macOS 10.15+, and Windows 7 and newer. Bitcoin Core should also work on most other Unix-like systems but is not as frequently tested on them. It is not recommended to use Bitcoin Core on unsupported systems. Notable changes =============== ### Gui - gui#774 Fix crash on selecting "Mask values" in transaction view ### RPC - #29003 rpc: fix getrawtransaction segfault ### Wallet - #29176 wallet: Fix use-after-free in WalletBatch::EraseRecords - #29510 wallet: `getrawchangeaddress` and `getnewaddress` failures should not affect keypools for descriptor wallets ### P2P and network changes - #29412 p2p: Don't process mutated blocks - #29524 p2p: Don't consider blocks mutated if they don't connect to known prev block Credits ======= Thanks to everyone who directly contributed to this release: - Martin Zumsande - Sebastian Falbesoner - MarcoFalke - UdjinM6 - dergoegge - Greg Sanders As well as to everyone that helped with translations on [Transifex](https://www.transifex.com/bitcoin/bitcoin/).
@ 47750177:8969e41a
2024-04-08 12:00:0025.2 Release Notes ================== Bitcoin Core version 25.2 is now available from: <https://bitcoincore.org/bin/bitcoin-core-25.2> This release includes various bug fixes and performance improvements, as well as updated translations. Please report bugs using the issue tracker at GitHub: <https://github.com/bitcoin/bitcoin/issues> To receive security and update notifications, please subscribe to: <https://bitcoincore.org/en/list/announcements/join/> How to Upgrade ============== If you are running an older version, shut it down. Wait until it has completely shut down (which might take a few minutes in some cases), then run the installer (on Windows) or just copy over `/Applications/Bitcoin-Qt` (on macOS) or `bitcoind`/`bitcoin-qt` (on Linux). Upgrading directly from a version of Bitcoin Core that has reached its EOL is possible, but it might take some time if the data directory needs to be migrated. Old wallet versions of Bitcoin Core are generally supported. Compatibility ============== Bitcoin Core is supported and extensively tested on operating systems using the Linux kernel, macOS 10.15+, and Windows 7 and newer. Bitcoin Core should also work on most other Unix-like systems but is not as frequently tested on them. It is not recommended to use Bitcoin Core on unsupported systems. Notable changes =============== ### Gui - gui#774 Fix crash on selecting "Mask values" in transaction view ### RPC - #29003 rpc: fix getrawtransaction segfault ### Wallet - #29176 wallet: Fix use-after-free in WalletBatch::EraseRecords - #29510 wallet: `getrawchangeaddress` and `getnewaddress` failures should not affect keypools for descriptor wallets ### P2P and network changes - #29412 p2p: Don't process mutated blocks - #29524 p2p: Don't consider blocks mutated if they don't connect to known prev block Credits ======= Thanks to everyone who directly contributed to this release: - Martin Zumsande - Sebastian Falbesoner - MarcoFalke - UdjinM6 - dergoegge - Greg Sanders As well as to everyone that helped with translations on [Transifex](https://www.transifex.com/bitcoin/bitcoin/). @ 3bf0c63f:aefa459d
2024-03-23 08:57:08# Nostr is not decentralized nor censorship-resistant Peter Todd has been [saying this](nostr:nevent1qqsq5zzu9ezhgq6es36jgg94wxsa2xh55p4tfa56yklsvjemsw7vj3cpp4mhxue69uhkummn9ekx7mqpr4mhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet5qy8hwumn8ghj7mn0wd68ytnddaksz9rhwden5te0dehhxarj9ehhsarj9ejx2aspzfmhxue69uhk7enxvd5xz6tw9ec82cspz3mhxue69uhhyetvv9ujuerpd46hxtnfduq3vamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmnyqy28wumn8ghj7un9d3shjtnwdaehgu3wvfnsz9nhwden5te0wfjkccte9ec8y6tdv9kzumn9wspzpn92tr3hexwgt0z7w4qz3fcch4ryshja8jeng453aj4c83646jxvxkyvs4) for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right. Nostr _today_ is indeed centralized. Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:  The top one was published to `wss://nostr.wine`, `wss://nos.lol`, `wss://pyramid.fiatjaf.com`. The second was published to the relay where I generally publish all my notes to, `wss://pyramid.fiatjaf.com`, and that is announced on my [NIP-05 file](https://fiatjaf.com/.well-known/nostr.json) and on my [NIP-65](https://nips.nostr.com/65) relay list. A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today: 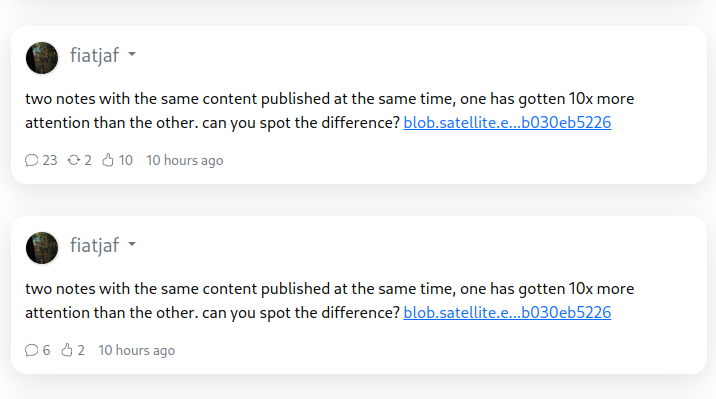 These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains. What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all. Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant. What happens is that most people who engaged with the note are _following me_, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on `wss://pyramid.fiatjaf.com`. If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before. Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today. Peter Todd is wrong that Nostr is _inherently_ centralized or that it needs a _protocol change_ to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we [drive in the right direction](nostr:naddr1qqykycekxd3nxdpcvgq3zamnwvaz7tmxd9shg6npvchxxmmdqgsrhuxx8l9ex335q7he0f09aej04zpazpl0ne2cgukyawd24mayt8grqsqqqa2803ksy8) we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary. --- See also: - [Censorship-resistant relay discovery in Nostr](nostr:naddr1qqykycekxd3nxdpcvgq3zamnwvaz7tmxd9shg6npvchxxmmdqgsrhuxx8l9ex335q7he0f09aej04zpazpl0ne2cgukyawd24mayt8grqsqqqa2803ksy8) - [A vision for content discovery and relay usage for basic social-networking in Nostr](nostr:naddr1qqyrxe33xqmxgve3qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cywwjvq)
@ 3bf0c63f:aefa459d
2024-03-23 08:57:08# Nostr is not decentralized nor censorship-resistant Peter Todd has been [saying this](nostr:nevent1qqsq5zzu9ezhgq6es36jgg94wxsa2xh55p4tfa56yklsvjemsw7vj3cpp4mhxue69uhkummn9ekx7mqpr4mhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet5qy8hwumn8ghj7mn0wd68ytnddaksz9rhwden5te0dehhxarj9ehhsarj9ejx2aspzfmhxue69uhk7enxvd5xz6tw9ec82cspz3mhxue69uhhyetvv9ujuerpd46hxtnfduq3vamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmnyqy28wumn8ghj7un9d3shjtnwdaehgu3wvfnsz9nhwden5te0wfjkccte9ec8y6tdv9kzumn9wspzpn92tr3hexwgt0z7w4qz3fcch4ryshja8jeng453aj4c83646jxvxkyvs4) for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right. Nostr _today_ is indeed centralized. Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:  The top one was published to `wss://nostr.wine`, `wss://nos.lol`, `wss://pyramid.fiatjaf.com`. The second was published to the relay where I generally publish all my notes to, `wss://pyramid.fiatjaf.com`, and that is announced on my [NIP-05 file](https://fiatjaf.com/.well-known/nostr.json) and on my [NIP-65](https://nips.nostr.com/65) relay list. A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today: 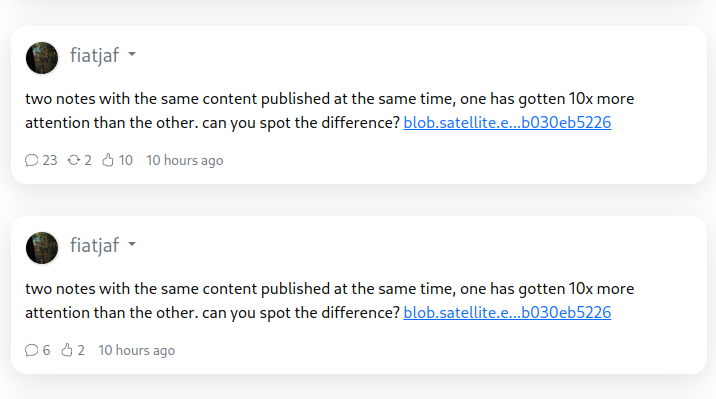 These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains. What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all. Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant. What happens is that most people who engaged with the note are _following me_, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on `wss://pyramid.fiatjaf.com`. If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before. Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today. Peter Todd is wrong that Nostr is _inherently_ centralized or that it needs a _protocol change_ to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we [drive in the right direction](nostr:naddr1qqykycekxd3nxdpcvgq3zamnwvaz7tmxd9shg6npvchxxmmdqgsrhuxx8l9ex335q7he0f09aej04zpazpl0ne2cgukyawd24mayt8grqsqqqa2803ksy8) we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary. --- See also: - [Censorship-resistant relay discovery in Nostr](nostr:naddr1qqykycekxd3nxdpcvgq3zamnwvaz7tmxd9shg6npvchxxmmdqgsrhuxx8l9ex335q7he0f09aej04zpazpl0ne2cgukyawd24mayt8grqsqqqa2803ksy8) - [A vision for content discovery and relay usage for basic social-networking in Nostr](nostr:naddr1qqyrxe33xqmxgve3qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cywwjvq) @ 6871d8df:4a9396c1
2024-02-24 22:42:16In an era where data seems to be as valuable as currency, the prevailing trend in AI starkly contrasts with the concept of personal data ownership. The explosion of AI and the ensuing race have made it easy to overlook where the data is coming from. The current model, dominated by big tech players, involves collecting vast amounts of user data and selling it to AI companies for training LLMs. Reddit recently penned a 60 million dollar deal, Google guards and mines Youtube, and more are going this direction. But is that their data to sell? Yes, it's on their platforms, but without the users to generate it, what would they monetize? To me, this practice raises significant ethical questions, as it assumes that user data is a commodity that companies can exploit at will. The heart of the issue lies in the ownership of data. Why, in today's digital age, do we not retain ownership of our data? Why can't our data follow us, under our control, to wherever we want to go? These questions echo the broader sentiment that while some in the tech industry — such as the blockchain-first crypto bros — recognize the importance of data ownership, their "blockchain for everything solutions," to me, fall significantly short in execution. Reddit further complicates this with its current move to IPO, which, on the heels of the large data deal, might reinforce the mistaken belief that user-generated data is a corporate asset. Others, no doubt, will follow suit. This underscores the urgent need for a paradigm shift towards recognizing and respecting user data as personal property. In my perfect world, the digital landscape would undergo a revolutionary transformation centered around the empowerment and sovereignty of individual data ownership. Platforms like Twitter, Reddit, Yelp, YouTube, and Stack Overflow, integral to our digital lives, would operate on a fundamentally different premise: user-owned data. In this envisioned future, data ownership would not just be a concept but a practice, with public and private keys ensuring the authenticity and privacy of individual identities. This model would eliminate the private data silos that currently dominate, where companies profit from selling user data without consent. Instead, data would traverse a decentralized protocol akin to the internet, prioritizing user control and transparency. The cornerstone of this world would be a meritocratic digital ecosystem. Success for companies would hinge on their ability to leverage user-owned data to deliver unparalleled value rather than their capacity to gatekeep and monetize information. If a company breaks my trust, I can move to a competitor, and my data, connections, and followers will come with me. This shift would herald an era where consent, privacy, and utility define the digital experience, ensuring that the benefits of technology are equitably distributed and aligned with the users' interests and rights. The conversation needs to shift fundamentally. We must challenge this trajectory and advocate for a future where data ownership and privacy are not just ideals but realities. If we continue on our current path without prioritizing individual data rights, the future of digital privacy and autonomy is bleak. Big tech's dominance allows them to treat user data as a commodity, potentially selling and exploiting it without consent. This imbalance has already led to users being cut off from their digital identities and connections when platforms terminate accounts, underscoring the need for a digital ecosystem that empowers user control over data. Without changing direction, we risk a future where our content — and our freedoms by consequence — are controlled by a few powerful entities, threatening our rights and the democratic essence of the digital realm. We must advocate for a shift towards data ownership by individuals to preserve our digital freedoms and democracy.
@ 6871d8df:4a9396c1
2024-02-24 22:42:16In an era where data seems to be as valuable as currency, the prevailing trend in AI starkly contrasts with the concept of personal data ownership. The explosion of AI and the ensuing race have made it easy to overlook where the data is coming from. The current model, dominated by big tech players, involves collecting vast amounts of user data and selling it to AI companies for training LLMs. Reddit recently penned a 60 million dollar deal, Google guards and mines Youtube, and more are going this direction. But is that their data to sell? Yes, it's on their platforms, but without the users to generate it, what would they monetize? To me, this practice raises significant ethical questions, as it assumes that user data is a commodity that companies can exploit at will. The heart of the issue lies in the ownership of data. Why, in today's digital age, do we not retain ownership of our data? Why can't our data follow us, under our control, to wherever we want to go? These questions echo the broader sentiment that while some in the tech industry — such as the blockchain-first crypto bros — recognize the importance of data ownership, their "blockchain for everything solutions," to me, fall significantly short in execution. Reddit further complicates this with its current move to IPO, which, on the heels of the large data deal, might reinforce the mistaken belief that user-generated data is a corporate asset. Others, no doubt, will follow suit. This underscores the urgent need for a paradigm shift towards recognizing and respecting user data as personal property. In my perfect world, the digital landscape would undergo a revolutionary transformation centered around the empowerment and sovereignty of individual data ownership. Platforms like Twitter, Reddit, Yelp, YouTube, and Stack Overflow, integral to our digital lives, would operate on a fundamentally different premise: user-owned data. In this envisioned future, data ownership would not just be a concept but a practice, with public and private keys ensuring the authenticity and privacy of individual identities. This model would eliminate the private data silos that currently dominate, where companies profit from selling user data without consent. Instead, data would traverse a decentralized protocol akin to the internet, prioritizing user control and transparency. The cornerstone of this world would be a meritocratic digital ecosystem. Success for companies would hinge on their ability to leverage user-owned data to deliver unparalleled value rather than their capacity to gatekeep and monetize information. If a company breaks my trust, I can move to a competitor, and my data, connections, and followers will come with me. This shift would herald an era where consent, privacy, and utility define the digital experience, ensuring that the benefits of technology are equitably distributed and aligned with the users' interests and rights. The conversation needs to shift fundamentally. We must challenge this trajectory and advocate for a future where data ownership and privacy are not just ideals but realities. If we continue on our current path without prioritizing individual data rights, the future of digital privacy and autonomy is bleak. Big tech's dominance allows them to treat user data as a commodity, potentially selling and exploiting it without consent. This imbalance has already led to users being cut off from their digital identities and connections when platforms terminate accounts, underscoring the need for a digital ecosystem that empowers user control over data. Without changing direction, we risk a future where our content — and our freedoms by consequence — are controlled by a few powerful entities, threatening our rights and the democratic essence of the digital realm. We must advocate for a shift towards data ownership by individuals to preserve our digital freedoms and democracy. @ 8ce092d8:950c24ad
2024-02-04 23:35:07# Overview 1. Introduction 2. Model Types 3. Training (Data Collection and Config Settings) 4. Probability Viewing: AI Inspector 5. Match 6. Cheat Sheet # I. Introduction AI Arena is the first game that combines human and artificial intelligence collaboration. AI learns your skills through "imitation learning." ## Official Resources 1. Official Documentation (Must Read): [Everything You Need to Know About AI Arena](https://docs.aiarena.io/everything-you-need-to-know) Watch the 2-minute video in the documentation to quickly understand the basic flow of the game. 2. Official Play-2-Airdrop competition FAQ Site https://aiarena.notion.site/aiarena/Gateway-to-the-Arena-52145e990925499d95f2fadb18a24ab0 3. Official Discord (Must Join): https://discord.gg/aiarenaplaytest for the latest announcements or seeking help. The team will also have a exclusive channel there. 4. Official YouTube: https://www.youtube.com/@aiarena because the game has built-in tutorials, you can choose to watch videos. ## What is this game about? 1. Although categorized as a platform fighting game, the core is a probability-based strategy game. 2. Warriors take actions based on probabilities on the AI Inspector dashboard, competing against opponents. 3. The game does not allow direct manual input of probabilities for each area but inputs information through data collection and establishes models by adjusting parameters. 4. Data collection emulates fighting games, but training can be completed using a Dummy As long as you can complete the in-game tutorial, you can master the game controls. # II. Model Types Before training, there are three model types to choose from: Simple Model Type, Original Model Type, and Advanced Model Type. **It is recommended to try the Advanced Model Type after completing at least one complete training with the Simple Model Type and gaining some understanding of the game.**  ## Simple Model Type The Simple Model is akin to completing a form, and the training session is comparable to filling various sections of that form. This model has 30 buckets. Each bucket can be seen as telling the warrior what action to take in a specific situation. There are 30 buckets, meaning 30 different scenarios. Within the same bucket, the probabilities for direction or action are the same. For example: What should I do when I'm off-stage — refer to the "Recovery (you off-stage)" bucket. **For all buckets, refer to this official documentation:** https://docs.aiarena.io/arenadex/game-mechanics/tabular-model-v2 **Video (no sound): The entire training process for all buckets** https://youtu.be/1rfRa3WjWEA Game version 2024.1.10. The method of saving is outdated. Please refer to the game updates. ## Advanced Model Type The "Original Model Type" and "Advanced Model Type" are based on Machine Learning, which is commonly referred to as combining with AI. The Original Model Type consists of only one bucket, representing the entire map. If you want the AI to learn different scenarios, you need to choose a "Focus Area" to let the warrior know where to focus. A single bucket means that a slight modification can have a widespread impact on the entire model. This is where the "Advanced Model Type" comes in. The "Advanced Model Type" can be seen as a combination of the "Original Model Type" and the "Simple Model Type". The Advanced Model Type divides the map into 8 buckets. Each bucket can use many "Focus Area." For a detailed explanation of the 8 buckets and different Focus Areas, please refer to the tutorial page (accessible in the Advanced Model Type, after completing a training session, at the top left of the Advanced Config, click on "Tutorial").  # III. Training (Data Collection and Config Settings) ## Training Process: 1. **Collect Data** 2. **Set Parameters, Train, and Save** 3. **Repeat Step 1 until the Model is Complete** Training the Simple Model Type is the easiest to start with; refer to the video above for a detailed process. Training the Advanced Model Type offers more possibilities through the combination of "Focus Area" parameters, providing a higher upper limit. While the Original Model Type has great potential, it's harder to control. Therefore, this section focuses on the "Advanced Model Type." ## 1. What Kind of Data to Collect 1. **High-Quality Data:** Collect purposeful data. Garbage in, garbage out. Only collect the necessary data; don't collect randomly. It's recommended to use Dummy to collect data. However, don't pursue perfection; through parameter adjustments, AI has a certain level of fault tolerance. 2. **Balanced Data:** Balance your dataset. In simple terms, if you complete actions on the left side a certain number of times, also complete a similar number on the right side. While data imbalance can be addressed through parameter adjustments (see below), it's advised not to have this issue during data collection. 3. **Moderate Amount:** A single training will include many individual actions. Collect data for each action 1-10 times. Personally, it's recommended to collect data 2-3 times for a single action. If the effect of a single training is not clear, conduct a second (or even third) training with the same content, but with different parameter settings. ## 2. What to Collect (and Focus Area Selection) Game actions mimic fighting games, consisting of 4 directions + 6 states (Idle, Jump, Attack, Grab, Special, Shield). Directions can be combined into ↗, ↘, etc. These directions and states can then be combined into different actions. To make "Focus Area" effective, you need to collect data in training that matches these parameters. For example, for "Distance to Opponent", you need to collect data when close to the opponent and also when far away. \* Note: While you can split into multiple training sessions, it's most effective to cover different situations within a single training. Refer to the Simple Config, categorize the actions you want to collect, and based on the game scenario, classify them into two categories: "Movement" and "Combat." 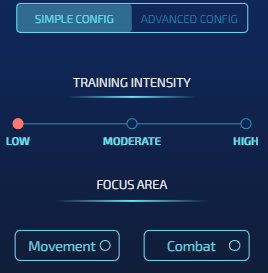 ### Movement-Based Actions #### Action Collection When the warrior is offstage, regardless of where the opponent is, we require the warrior to return to the stage to prevent self-destruction. This involves 3 aerial buckets: 5 (Near Blast Zone), 7 (Under Stage), and 8 (Side Of Stage).  \* Note: The background comes from the Tutorial mentioned earlier. The arrows in the image indicate the direction of the action and are for reference only. \* Note: Action collection should be clean; do not collect actions that involve leaving the stage. #### Config Settings In the Simple Config, you can directly choose "Movement" in it. However, for better customization, it's recommended to use the Advanced Config directly. - Intensity: The method for setting Intensity will be introduced separately later. - Buckets: As shown in the image, choose the bucket you are training. - Focus Area: Position-based parameters: - Your position (must) - Raycast Platform Distance, Raycast Platform Type (optional, generally choose these in Bucket 7) ### Combat-Based Actions **The goal is to direct attacks quickly and effectively towards the opponent, which is the core of game strategy.** This involves 5 buckets: - 2 regular situations - In the air: 6 (Safe Zone) - On the ground: 4 (Opponent Active) - 3 special situations on the ground: - 1 Projectile Active - 2 Opponent Knockback - 3 Opponent Stunned #### 2 Regular Situations  In the in-game tutorial, we learned how to perform horizontal attacks. However, in the actual game, directions expand to 8 dimensions. Imagine having 8 relative positions available for launching hits against the opponent. Our task is to design what action to use for attack or defense at each relative position. **Focus Area** - Basic (generally select all) - Angle to opponent - Distance to opponent - Discrete Distance: Choosing this option helps better differentiate between closer and farther distances from the opponent. As shown in the image, red indicates a relatively close distance, and green indicates a relatively distant distance. - Advanced: Other commonly used parameters - Direction: different facings to opponent - Your Elemental Gauge and Discrete Elementals: Considering the special's charge - Opponent action: The warrior will react based on the opponent's different actions. - Your action: Your previous action. Choose this if teaching combos. #### 3 Special Situations on the Ground Projectile Active, Opponent Stunned, Opponent Knockback These three buckets can be referenced in the Simple Model Type video. The parameter settings approach is the same as Opponent Active/Safe Zone. For Projectile Active, in addition to the parameters based on combat, to track the projectile, you also need to select "Raycast Projectile Distance" and "Raycast Projectile On Target." ### 3. Setting "Intensity" #### Resources - The "Tutorial" mentioned earlier explains these parameters. - Official Config Document (2022.12.24): https://docs.google.com/document/d/1adXwvDHEnrVZ5bUClWQoBQ8ETrSSKgG5q48YrogaFJs/edit --- #### TL;DR: **Epochs:** - Adjust to fewer epochs if learning is insufficient, increase for more learning. **Batch Size:** - Set to the minimum (16) if data is precise but unbalanced, or just want it to learn fast - Increase (e.g., 64) if data is slightly imprecise but balanced. - If both imprecise and unbalanced, consider retraining. **Learning Rate:** - Maximize (0.01) for more learning but a risk of forgetting past knowledge. - Minimize for more accurate learning with less impact on previous knowledge. **Lambda:** - Reduce for prioritizing learning new things. **Data Cleaning:** - Enable "Remove Sparsity" unless you want AI to learn idleness. - For special cases, like teaching the warrior to use special moves when idle, refer to this tutorial video: https://discord.com/channels/1140682688651612291/1140683283626201098/1195467295913431111 **Personal Experience:** - Initial training with settings: 125 epochs, batch size 16, learning rate 0.01, lambda 0, data cleaning enabled. - Prioritize Multistream, sometimes use Oversampling. - Fine-tune subsequent training based on the mentioned theories. # IV. Probability Viewing: AI Inspector The dashboard consists of "Direction + Action." Above the dashboard, you can see the "Next Action" – the action the warrior will take in its current state. The higher the probability, the more likely the warrior is to perform that action, indicating a quicker reaction. It's essential to note that when checking the Direction, the one with the highest visual representation may not have the highest numerical value. To determine the actual value, hover the mouse over the graphical representation, as shown below, where the highest direction is "Idle."  In the map, you can drag the warrior to view the probabilities of the warrior in different positions. Right-click on the warrior with the mouse to change the warrior's facing. The status bar below can change the warrior's state on the map.  When training the "Opponent Stunned, Opponent Knockback" bucket, you need to select the status below the opponent's status bar. If you are focusing on "Opponent action" in the Focus Zone, choose the action in the opponent's status bar. If you are focusing on "Your action" in the Focus Zone, choose the action in your own status bar. When training the "Projectile Active" Bucket, drag the projectile on the right side of the dashboard to check the status. **Next** The higher the probability, the faster the reaction. However, be cautious when the action probability reaches 100%. This may cause the warrior to be in a special case of "State Transition," resulting in unnecessary "Idle" states. > Explanation: > In each state a fighter is in, there are different "possible transitions". For example, from falling state you cannot do low sweep because low sweep requires you to be on the ground. For the shield state, we do not allow you to directly transition to headbutt. So to do headbutt you have to first exit to another state and then do it from there (assuming that state allows you to do headbutt). This is the reason the fighter runs because "run" action is a valid state transition from shield. [Source](https://discord.com/channels/848599369879388170/1079903287760928819/1160049804844470292) # V. Learn from Matches After completing all the training, your model is preliminarily finished—congratulations! The warrior will step onto the arena alone and embark on its debut! Next, we will learn about the strengths and weaknesses of the warrior from battles to continue refining the warrior's model. In matches, besides appreciating the performance, pay attention to the following: 1. **Movement, i.e., Off the Stage:** Observe how the warrior gets eliminated. Is it due to issues in the action settings at a certain position, or is it a normal death caused by a high percentage? The former is what we need to avoid and optimize. 2. **Combat:** Analyze both sides' actions carefully. Observe which actions you and the opponent used in different states. Check which of your hits are less effective, and how does the opponent handle different actions, etc. The approach to battle analysis is similar to the thought process in the "Training", helping to have a more comprehensive understanding of the warrior's performance and making targeted improvements. # VI. Cheat Sheet **Training** 1. Click "Collect" to collect actions. 2. "Map - Data Limit" is more user-friendly. Most players perform initial training on the "Arena" map. 3. Switch between the warrior and the dummy: Tab key (keyboard) / Home key (controller). 4. Use "Collect" to make the opponent loop a set of actions. 5. Instantly move the warrior to a specific location: Click "Settings" - SPAWN - Choose the desired location on the map - On. Press the Enter key (keyboard) / Start key (controller) during training. **Inspector** 1. Right-click on the fighter to change their direction. Drag the fighter and observe the changes in different positions and directions. 2. When satisfied with the training, click "Save." 3. In "Sparring" and "Simulation," use "Current Working Model." 4. If satisfied with a model, then click "compete." The model used in the rankings is the one marked as "competing." **Sparring / Ranked** 1. Use the Throneroom map only for the top 2 or top 10 rankings. 2. There is a 30-second cooldown between matches. The replays are played for any match. Once the battle begins, you can see the winner on the leaderboard or by right-clicking the page - Inspect - Console. Also, if you encounter any errors or bugs, please send screenshots of the console to the Discord server. Good luck! See you on the arena!
@ 8ce092d8:950c24ad
2024-02-04 23:35:07# Overview 1. Introduction 2. Model Types 3. Training (Data Collection and Config Settings) 4. Probability Viewing: AI Inspector 5. Match 6. Cheat Sheet # I. Introduction AI Arena is the first game that combines human and artificial intelligence collaboration. AI learns your skills through "imitation learning." ## Official Resources 1. Official Documentation (Must Read): [Everything You Need to Know About AI Arena](https://docs.aiarena.io/everything-you-need-to-know) Watch the 2-minute video in the documentation to quickly understand the basic flow of the game. 2. Official Play-2-Airdrop competition FAQ Site https://aiarena.notion.site/aiarena/Gateway-to-the-Arena-52145e990925499d95f2fadb18a24ab0 3. Official Discord (Must Join): https://discord.gg/aiarenaplaytest for the latest announcements or seeking help. The team will also have a exclusive channel there. 4. Official YouTube: https://www.youtube.com/@aiarena because the game has built-in tutorials, you can choose to watch videos. ## What is this game about? 1. Although categorized as a platform fighting game, the core is a probability-based strategy game. 2. Warriors take actions based on probabilities on the AI Inspector dashboard, competing against opponents. 3. The game does not allow direct manual input of probabilities for each area but inputs information through data collection and establishes models by adjusting parameters. 4. Data collection emulates fighting games, but training can be completed using a Dummy As long as you can complete the in-game tutorial, you can master the game controls. # II. Model Types Before training, there are three model types to choose from: Simple Model Type, Original Model Type, and Advanced Model Type. **It is recommended to try the Advanced Model Type after completing at least one complete training with the Simple Model Type and gaining some understanding of the game.**  ## Simple Model Type The Simple Model is akin to completing a form, and the training session is comparable to filling various sections of that form. This model has 30 buckets. Each bucket can be seen as telling the warrior what action to take in a specific situation. There are 30 buckets, meaning 30 different scenarios. Within the same bucket, the probabilities for direction or action are the same. For example: What should I do when I'm off-stage — refer to the "Recovery (you off-stage)" bucket. **For all buckets, refer to this official documentation:** https://docs.aiarena.io/arenadex/game-mechanics/tabular-model-v2 **Video (no sound): The entire training process for all buckets** https://youtu.be/1rfRa3WjWEA Game version 2024.1.10. The method of saving is outdated. Please refer to the game updates. ## Advanced Model Type The "Original Model Type" and "Advanced Model Type" are based on Machine Learning, which is commonly referred to as combining with AI. The Original Model Type consists of only one bucket, representing the entire map. If you want the AI to learn different scenarios, you need to choose a "Focus Area" to let the warrior know where to focus. A single bucket means that a slight modification can have a widespread impact on the entire model. This is where the "Advanced Model Type" comes in. The "Advanced Model Type" can be seen as a combination of the "Original Model Type" and the "Simple Model Type". The Advanced Model Type divides the map into 8 buckets. Each bucket can use many "Focus Area." For a detailed explanation of the 8 buckets and different Focus Areas, please refer to the tutorial page (accessible in the Advanced Model Type, after completing a training session, at the top left of the Advanced Config, click on "Tutorial").  # III. Training (Data Collection and Config Settings) ## Training Process: 1. **Collect Data** 2. **Set Parameters, Train, and Save** 3. **Repeat Step 1 until the Model is Complete** Training the Simple Model Type is the easiest to start with; refer to the video above for a detailed process. Training the Advanced Model Type offers more possibilities through the combination of "Focus Area" parameters, providing a higher upper limit. While the Original Model Type has great potential, it's harder to control. Therefore, this section focuses on the "Advanced Model Type." ## 1. What Kind of Data to Collect 1. **High-Quality Data:** Collect purposeful data. Garbage in, garbage out. Only collect the necessary data; don't collect randomly. It's recommended to use Dummy to collect data. However, don't pursue perfection; through parameter adjustments, AI has a certain level of fault tolerance. 2. **Balanced Data:** Balance your dataset. In simple terms, if you complete actions on the left side a certain number of times, also complete a similar number on the right side. While data imbalance can be addressed through parameter adjustments (see below), it's advised not to have this issue during data collection. 3. **Moderate Amount:** A single training will include many individual actions. Collect data for each action 1-10 times. Personally, it's recommended to collect data 2-3 times for a single action. If the effect of a single training is not clear, conduct a second (or even third) training with the same content, but with different parameter settings. ## 2. What to Collect (and Focus Area Selection) Game actions mimic fighting games, consisting of 4 directions + 6 states (Idle, Jump, Attack, Grab, Special, Shield). Directions can be combined into ↗, ↘, etc. These directions and states can then be combined into different actions. To make "Focus Area" effective, you need to collect data in training that matches these parameters. For example, for "Distance to Opponent", you need to collect data when close to the opponent and also when far away. \* Note: While you can split into multiple training sessions, it's most effective to cover different situations within a single training. Refer to the Simple Config, categorize the actions you want to collect, and based on the game scenario, classify them into two categories: "Movement" and "Combat." 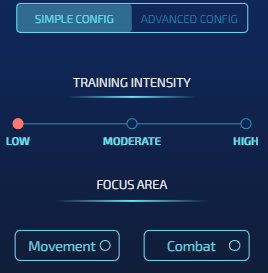 ### Movement-Based Actions #### Action Collection When the warrior is offstage, regardless of where the opponent is, we require the warrior to return to the stage to prevent self-destruction. This involves 3 aerial buckets: 5 (Near Blast Zone), 7 (Under Stage), and 8 (Side Of Stage).  \* Note: The background comes from the Tutorial mentioned earlier. The arrows in the image indicate the direction of the action and are for reference only. \* Note: Action collection should be clean; do not collect actions that involve leaving the stage. #### Config Settings In the Simple Config, you can directly choose "Movement" in it. However, for better customization, it's recommended to use the Advanced Config directly. - Intensity: The method for setting Intensity will be introduced separately later. - Buckets: As shown in the image, choose the bucket you are training. - Focus Area: Position-based parameters: - Your position (must) - Raycast Platform Distance, Raycast Platform Type (optional, generally choose these in Bucket 7) ### Combat-Based Actions **The goal is to direct attacks quickly and effectively towards the opponent, which is the core of game strategy.** This involves 5 buckets: - 2 regular situations - In the air: 6 (Safe Zone) - On the ground: 4 (Opponent Active) - 3 special situations on the ground: - 1 Projectile Active - 2 Opponent Knockback - 3 Opponent Stunned #### 2 Regular Situations  In the in-game tutorial, we learned how to perform horizontal attacks. However, in the actual game, directions expand to 8 dimensions. Imagine having 8 relative positions available for launching hits against the opponent. Our task is to design what action to use for attack or defense at each relative position. **Focus Area** - Basic (generally select all) - Angle to opponent - Distance to opponent - Discrete Distance: Choosing this option helps better differentiate between closer and farther distances from the opponent. As shown in the image, red indicates a relatively close distance, and green indicates a relatively distant distance. - Advanced: Other commonly used parameters - Direction: different facings to opponent - Your Elemental Gauge and Discrete Elementals: Considering the special's charge - Opponent action: The warrior will react based on the opponent's different actions. - Your action: Your previous action. Choose this if teaching combos. #### 3 Special Situations on the Ground Projectile Active, Opponent Stunned, Opponent Knockback These three buckets can be referenced in the Simple Model Type video. The parameter settings approach is the same as Opponent Active/Safe Zone. For Projectile Active, in addition to the parameters based on combat, to track the projectile, you also need to select "Raycast Projectile Distance" and "Raycast Projectile On Target." ### 3. Setting "Intensity" #### Resources - The "Tutorial" mentioned earlier explains these parameters. - Official Config Document (2022.12.24): https://docs.google.com/document/d/1adXwvDHEnrVZ5bUClWQoBQ8ETrSSKgG5q48YrogaFJs/edit --- #### TL;DR: **Epochs:** - Adjust to fewer epochs if learning is insufficient, increase for more learning. **Batch Size:** - Set to the minimum (16) if data is precise but unbalanced, or just want it to learn fast - Increase (e.g., 64) if data is slightly imprecise but balanced. - If both imprecise and unbalanced, consider retraining. **Learning Rate:** - Maximize (0.01) for more learning but a risk of forgetting past knowledge. - Minimize for more accurate learning with less impact on previous knowledge. **Lambda:** - Reduce for prioritizing learning new things. **Data Cleaning:** - Enable "Remove Sparsity" unless you want AI to learn idleness. - For special cases, like teaching the warrior to use special moves when idle, refer to this tutorial video: https://discord.com/channels/1140682688651612291/1140683283626201098/1195467295913431111 **Personal Experience:** - Initial training with settings: 125 epochs, batch size 16, learning rate 0.01, lambda 0, data cleaning enabled. - Prioritize Multistream, sometimes use Oversampling. - Fine-tune subsequent training based on the mentioned theories. # IV. Probability Viewing: AI Inspector The dashboard consists of "Direction + Action." Above the dashboard, you can see the "Next Action" – the action the warrior will take in its current state. The higher the probability, the more likely the warrior is to perform that action, indicating a quicker reaction. It's essential to note that when checking the Direction, the one with the highest visual representation may not have the highest numerical value. To determine the actual value, hover the mouse over the graphical representation, as shown below, where the highest direction is "Idle."  In the map, you can drag the warrior to view the probabilities of the warrior in different positions. Right-click on the warrior with the mouse to change the warrior's facing. The status bar below can change the warrior's state on the map.  When training the "Opponent Stunned, Opponent Knockback" bucket, you need to select the status below the opponent's status bar. If you are focusing on "Opponent action" in the Focus Zone, choose the action in the opponent's status bar. If you are focusing on "Your action" in the Focus Zone, choose the action in your own status bar. When training the "Projectile Active" Bucket, drag the projectile on the right side of the dashboard to check the status. **Next** The higher the probability, the faster the reaction. However, be cautious when the action probability reaches 100%. This may cause the warrior to be in a special case of "State Transition," resulting in unnecessary "Idle" states. > Explanation: > In each state a fighter is in, there are different "possible transitions". For example, from falling state you cannot do low sweep because low sweep requires you to be on the ground. For the shield state, we do not allow you to directly transition to headbutt. So to do headbutt you have to first exit to another state and then do it from there (assuming that state allows you to do headbutt). This is the reason the fighter runs because "run" action is a valid state transition from shield. [Source](https://discord.com/channels/848599369879388170/1079903287760928819/1160049804844470292) # V. Learn from Matches After completing all the training, your model is preliminarily finished—congratulations! The warrior will step onto the arena alone and embark on its debut! Next, we will learn about the strengths and weaknesses of the warrior from battles to continue refining the warrior's model. In matches, besides appreciating the performance, pay attention to the following: 1. **Movement, i.e., Off the Stage:** Observe how the warrior gets eliminated. Is it due to issues in the action settings at a certain position, or is it a normal death caused by a high percentage? The former is what we need to avoid and optimize. 2. **Combat:** Analyze both sides' actions carefully. Observe which actions you and the opponent used in different states. Check which of your hits are less effective, and how does the opponent handle different actions, etc. The approach to battle analysis is similar to the thought process in the "Training", helping to have a more comprehensive understanding of the warrior's performance and making targeted improvements. # VI. Cheat Sheet **Training** 1. Click "Collect" to collect actions. 2. "Map - Data Limit" is more user-friendly. Most players perform initial training on the "Arena" map. 3. Switch between the warrior and the dummy: Tab key (keyboard) / Home key (controller). 4. Use "Collect" to make the opponent loop a set of actions. 5. Instantly move the warrior to a specific location: Click "Settings" - SPAWN - Choose the desired location on the map - On. Press the Enter key (keyboard) / Start key (controller) during training. **Inspector** 1. Right-click on the fighter to change their direction. Drag the fighter and observe the changes in different positions and directions. 2. When satisfied with the training, click "Save." 3. In "Sparring" and "Simulation," use "Current Working Model." 4. If satisfied with a model, then click "compete." The model used in the rankings is the one marked as "competing." **Sparring / Ranked** 1. Use the Throneroom map only for the top 2 or top 10 rankings. 2. There is a 30-second cooldown between matches. The replays are played for any match. Once the battle begins, you can see the winner on the leaderboard or by right-clicking the page - Inspect - Console. Also, if you encounter any errors or bugs, please send screenshots of the console to the Discord server. Good luck! See you on the arena! @ 3bf0c63f:aefa459d
2024-01-15 11:15:06# Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados - **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente. - **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados. - **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua. - **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer. - **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos. - **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas. - **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade). - **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis. - **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade. - **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho. - **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho. - **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma. - **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças. - **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família. - **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente. - **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo). - **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas. - **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente). - **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica. - **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar. - **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico. - **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais. - **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil). - **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória. - **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles. - **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas. - **inflação**: a inflação estimula o endividamento e o consumismo. - **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas. - **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo.
@ 3bf0c63f:aefa459d
2024-01-15 11:15:06# Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados - **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente. - **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados. - **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua. - **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer. - **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos. - **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas. - **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade). - **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis. - **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade. - **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho. - **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho. - **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma. - **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças. - **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família. - **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente. - **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo). - **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas. - **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente). - **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica. - **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar. - **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico. - **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais. - **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil). - **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória. - **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles. - **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas. - **inflação**: a inflação estimula o endividamento e o consumismo. - **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas. - **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo. @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# IPFS problems: Community I was an avid IPFS user until yesterday. Many many times I asked simple questions for which I couldn't find an answer on the internet in the #ipfs IRC channel on Freenode. Most of the times I didn't get an answer, and even when I got it was rarely by someone who knew IPFS deeply. I've had issues go unanswered on js-ipfs repositories for year – one of these was raising awareness of a problem that then got fixed some months later by a complete rewrite, I closed my own issue after realizing that by myself some couple of months later, I don't think the people responsible for the rewrite were ever acknowledge that he had fixed my issue. Some days ago I asked some questions about how the IPFS protocol worked internally, sincerely trying to understand the inefficiencies in finding and fetching content over IPFS. I pointed it would be a good idea to have a drawing showing that so people would understand the difficulties (which I didn't) and wouldn't be pissed off by the slowness. I was told to read the whitepaper. I had already the whitepaper, but read again the relevant parts. The whitepaper doesn't explain anything about the DHT and how IPFS finds content. I said that in the room, was told to read again. Before anyone misread this section, I want to say I understand it's a pain to keep answering people on IRC if you're busy developing stuff of interplanetary importance, and that I'm not paying anyone nor I have the right to be answered. On the other hand, if you're developing a super-important protocol, financed by many millions of dollars and a lot of people are hitting their heads against your software and there's no one to help them; you're always busy but never delivers anything that brings joy to your users, something is very wrong. I sincerely don't know what IPFS developers are working on, I wouldn't doubt they're working on important things if they said that, but what I see – and what many other users see (take a look at the IPFS Discourse forum) is bugs, bugs all over the place, confusing UX, and almost no help.
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# IPFS problems: Community I was an avid IPFS user until yesterday. Many many times I asked simple questions for which I couldn't find an answer on the internet in the #ipfs IRC channel on Freenode. Most of the times I didn't get an answer, and even when I got it was rarely by someone who knew IPFS deeply. I've had issues go unanswered on js-ipfs repositories for year – one of these was raising awareness of a problem that then got fixed some months later by a complete rewrite, I closed my own issue after realizing that by myself some couple of months later, I don't think the people responsible for the rewrite were ever acknowledge that he had fixed my issue. Some days ago I asked some questions about how the IPFS protocol worked internally, sincerely trying to understand the inefficiencies in finding and fetching content over IPFS. I pointed it would be a good idea to have a drawing showing that so people would understand the difficulties (which I didn't) and wouldn't be pissed off by the slowness. I was told to read the whitepaper. I had already the whitepaper, but read again the relevant parts. The whitepaper doesn't explain anything about the DHT and how IPFS finds content. I said that in the room, was told to read again. Before anyone misread this section, I want to say I understand it's a pain to keep answering people on IRC if you're busy developing stuff of interplanetary importance, and that I'm not paying anyone nor I have the right to be answered. On the other hand, if you're developing a super-important protocol, financed by many millions of dollars and a lot of people are hitting their heads against your software and there's no one to help them; you're always busy but never delivers anything that brings joy to your users, something is very wrong. I sincerely don't know what IPFS developers are working on, I wouldn't doubt they're working on important things if they said that, but what I see – and what many other users see (take a look at the IPFS Discourse forum) is bugs, bugs all over the place, confusing UX, and almost no help. @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# Castas hindus em nova chave Shudras buscam o máximo bem para os seus próprios corpos; vaishyas o máximo bem para a sua própria vida terrena e a da sua família; kshatriyas o máximo bem para a sociedade e este mundo terreno; brâmanes buscam o máximo bem.
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# Castas hindus em nova chave Shudras buscam o máximo bem para os seus próprios corpos; vaishyas o máximo bem para a sua própria vida terrena e a da sua família; kshatriyas o máximo bem para a sociedade e este mundo terreno; brâmanes buscam o máximo bem. @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# Thoughts on Nostr key management On [Why I don't like NIP-26 as a solution for key management](nostr:naddr1qqyrgceh89nxgdmzqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823ctgmx78) I talked about multiple techniques that could be used to tackle the problem of key management on Nostr. Here are some ideas that work in tandem: - [NIP-41](https://github.com/nostr-protocol/nips/blob/master/41.md) (stateless key invalidation) - [NIP-46](https://github.com/nostr-protocol/nips/blob/master/46.md) (Nostr Connect) - [NIP-07](https://github.com/nostr-protocol/nips/blob/master/07.md) (signer browser extension) - [Connected hardware signing devices](https://lnbits.github.io/nostr-signing-device/installer/) - other things like musig or frostr keys used in conjunction with a semi-trusted server; or other kinds of trusted software, like a dedicated signer on a mobile device that can sign on behalf of other apps; or even a separate protocol that some people decide to use as the source of truth for their keys, and some clients might decide to use that automatically - there are probably many other ideas Some premises I have in my mind (that may be flawed) that base my thoughts on these matters (and cause me to not worry too much) are that - For the vast majority of people, Nostr keys aren't a target as valuable as Bitcoin keys, so they will probably be ok even without any solution; - Even when you lose everything, identity can be recovered -- slowly and painfully, but still --, unlike money; - Nostr is not trying to replace all other forms of online communication (even though when I think about this I can't imagine one thing that wouldn't be nice to replace with Nostr) or of offline communication, so there will always be ways. - For the vast majority of people, losing keys and starting fresh isn't a big deal. It is a big deal when you have followers and an online persona and your life depends on that, but how many people are like that? In the real world I see people deleting social media accounts all the time and creating new ones, people losing their phone numbers or other accounts associated with their phone numbers, and not caring very much -- they just find a way to notify friends and family and move on. We can probably come up with some specs to ease the "manual" recovery process, like social attestation and explicit signaling -- i.e., Alice, Bob and Carol are friends; Alice loses her key; Bob sends a new Nostr event kind to the network saying what is Alice's new key; depending on how much Carol trusts Bob, she can automatically start following that and remove the old key -- or something like that. --- One nice thing about some of these proposals, like NIP-41, or the social-recovery method, or the external-source-of-truth-method, is that they don't have to be implemented in any client, they can live in standalone single-purpose microapps that users open or visit only every now and then, and these can then automatically update their follow lists with the latest news from keys that have changed according to multiple methods.
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# Thoughts on Nostr key management On [Why I don't like NIP-26 as a solution for key management](nostr:naddr1qqyrgceh89nxgdmzqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823ctgmx78) I talked about multiple techniques that could be used to tackle the problem of key management on Nostr. Here are some ideas that work in tandem: - [NIP-41](https://github.com/nostr-protocol/nips/blob/master/41.md) (stateless key invalidation) - [NIP-46](https://github.com/nostr-protocol/nips/blob/master/46.md) (Nostr Connect) - [NIP-07](https://github.com/nostr-protocol/nips/blob/master/07.md) (signer browser extension) - [Connected hardware signing devices](https://lnbits.github.io/nostr-signing-device/installer/) - other things like musig or frostr keys used in conjunction with a semi-trusted server; or other kinds of trusted software, like a dedicated signer on a mobile device that can sign on behalf of other apps; or even a separate protocol that some people decide to use as the source of truth for their keys, and some clients might decide to use that automatically - there are probably many other ideas Some premises I have in my mind (that may be flawed) that base my thoughts on these matters (and cause me to not worry too much) are that - For the vast majority of people, Nostr keys aren't a target as valuable as Bitcoin keys, so they will probably be ok even without any solution; - Even when you lose everything, identity can be recovered -- slowly and painfully, but still --, unlike money; - Nostr is not trying to replace all other forms of online communication (even though when I think about this I can't imagine one thing that wouldn't be nice to replace with Nostr) or of offline communication, so there will always be ways. - For the vast majority of people, losing keys and starting fresh isn't a big deal. It is a big deal when you have followers and an online persona and your life depends on that, but how many people are like that? In the real world I see people deleting social media accounts all the time and creating new ones, people losing their phone numbers or other accounts associated with their phone numbers, and not caring very much -- they just find a way to notify friends and family and move on. We can probably come up with some specs to ease the "manual" recovery process, like social attestation and explicit signaling -- i.e., Alice, Bob and Carol are friends; Alice loses her key; Bob sends a new Nostr event kind to the network saying what is Alice's new key; depending on how much Carol trusts Bob, she can automatically start following that and remove the old key -- or something like that. --- One nice thing about some of these proposals, like NIP-41, or the social-recovery method, or the external-source-of-truth-method, is that they don't have to be implemented in any client, they can live in standalone single-purpose microapps that users open or visit only every now and then, and these can then automatically update their follow lists with the latest news from keys that have changed according to multiple methods. @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# IPFS problems: Shitcoinery IPFS was advertised to the Ethereum community since the beggining as a way to "store" data for their "dApps". I don't think this is harmful in any way, but for some reason it may have led IPFS developers to focus too much on Ethereum stuff. Once I watched a talk showing libp2p developers – despite being ignored by the Ethereum team (that ended up creating their own agnostic p2p library) – dedicating an enourmous amount of work on getting a libp2p app running in the browser talking to a normal Ethereum node. The always somewhat-abandoned "Awesome IPFS" site is a big repository of "dApps", some of which don't even have their landing page up anymore, useless Ethereum smart contracts that for some reason use IPFS to store whatever the useless data their users produce. Again, per se it isn't a problem that Ethereum people are using IPFS, but it is at least confusing, maybe misleading, that when you search for IPFS most of the use-cases are actually Ethereum useless-cases. ## See also * [Bitcoin](nostr:naddr1qqyryveexumnyd3kqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c7nywz4), the only non-shitcoin
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# IPFS problems: Shitcoinery IPFS was advertised to the Ethereum community since the beggining as a way to "store" data for their "dApps". I don't think this is harmful in any way, but for some reason it may have led IPFS developers to focus too much on Ethereum stuff. Once I watched a talk showing libp2p developers – despite being ignored by the Ethereum team (that ended up creating their own agnostic p2p library) – dedicating an enourmous amount of work on getting a libp2p app running in the browser talking to a normal Ethereum node. The always somewhat-abandoned "Awesome IPFS" site is a big repository of "dApps", some of which don't even have their landing page up anymore, useless Ethereum smart contracts that for some reason use IPFS to store whatever the useless data their users produce. Again, per se it isn't a problem that Ethereum people are using IPFS, but it is at least confusing, maybe misleading, that when you search for IPFS most of the use-cases are actually Ethereum useless-cases. ## See also * [Bitcoin](nostr:naddr1qqyryveexumnyd3kqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c7nywz4), the only non-shitcoin @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# Economics Just a bunch of somewhat-related notes. * [notes on "Economic Action Beyond the Extent of the Market", Per Bylund](nostr:naddr1qqyxxepsx3skgvenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cf5cy3p) * [Mises' interest rate theory](nostr:naddr1qqyr2dtrxycr2dmrqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c97asm3) * [Profits, not wages, as the originary factor](nostr:naddr1qqyrge3hxa3rqce4qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c7x67pu) * [Reisman on opportunity cost](nostr:naddr1qqyrswtr89nxvepkqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cwx7t3v) * [Money Supply Measurement](nostr:naddr1qqyr2v3cxcunserzqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cya65m9) * [Per Bylund's insight](nostr:naddr1qqyxvdtzxscxzcenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cuq3unj) * [Maybe a new approach to the Austrian Business Cycle Theory, some disorganized thoughts](nostr:naddr1qqyrvdecvccxxcejqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cl9wc86) * [An argument according to which fractional-reserve banking is merely theft and nothing else](nostr:naddr1qqyrywt9v5exydenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cfks90r) * [Conjecture and criticism](nostr:naddr1qqyrqde5x9snqvfnqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823ce4glh8) * [Qual é o economista? (piadas)](nostr:naddr1qqyx2vmrx93xgdpjqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c0ckmsx) * [UBI calculations](nostr:naddr1qqyryenpxe3ryvf4qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cuurj42) * [Donations on the internet](nostr:naddr1qqyrqwp4xsmnsvtxqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cex8903)
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# Economics Just a bunch of somewhat-related notes. * [notes on "Economic Action Beyond the Extent of the Market", Per Bylund](nostr:naddr1qqyxxepsx3skgvenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cf5cy3p) * [Mises' interest rate theory](nostr:naddr1qqyr2dtrxycr2dmrqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c97asm3) * [Profits, not wages, as the originary factor](nostr:naddr1qqyrge3hxa3rqce4qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c7x67pu) * [Reisman on opportunity cost](nostr:naddr1qqyrswtr89nxvepkqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cwx7t3v) * [Money Supply Measurement](nostr:naddr1qqyr2v3cxcunserzqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cya65m9) * [Per Bylund's insight](nostr:naddr1qqyxvdtzxscxzcenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cuq3unj) * [Maybe a new approach to the Austrian Business Cycle Theory, some disorganized thoughts](nostr:naddr1qqyrvdecvccxxcejqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cl9wc86) * [An argument according to which fractional-reserve banking is merely theft and nothing else](nostr:naddr1qqyrywt9v5exydenqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cfks90r) * [Conjecture and criticism](nostr:naddr1qqyrqde5x9snqvfnqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823ce4glh8) * [Qual é o economista? (piadas)](nostr:naddr1qqyx2vmrx93xgdpjqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823c0ckmsx) * [UBI calculations](nostr:naddr1qqyryenpxe3ryvf4qyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cuurj42) * [Donations on the internet](nostr:naddr1qqyrqwp4xsmnsvtxqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cex8903) @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# tempreites My first library to get stars on GitHub, was a very stupid templating library that used just HTML and HTML attributes ("DSL-free"). I was inspired by <http://microjs.com/> at the time and ended up not using the library. Probably no one ever did. - <https://github.com/fiatjaf/tempreites>
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# tempreites My first library to get stars on GitHub, was a very stupid templating library that used just HTML and HTML attributes ("DSL-free"). I was inspired by <http://microjs.com/> at the time and ended up not using the library. Probably no one ever did. - <https://github.com/fiatjaf/tempreites> @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# nix Pra instalar o [neuron](797984e3.md) fui forçado a baixar e instalar o [nix](https://nixos.org/download.html). Não consegui me lembrar por que não estava usando até hoje aquele maravilhoso sistema de instalar pacotes desde a primeira vez que tentei, anos atrás. Que sofrimento pra fazer funcionar com o `fish`, mas até que bem menos sofrimento que da outra vez. Tive que instalar um tal de `fish-foreign-environment` (usando o próprio nix!, já que a outra opção era o `oh-my-fish` ou qualquer outra porcaria dessas) e aí usá-lo para aplicar as definições de shell para bash direto no `fish`. E aí lembrei também que o `/nix/store` fica cheio demais, o negócio instala tudo que existe neste mundo a partir do zero. É só para computadores muito ricos, mas vamos ver como vai ser. Estou gostando do neuron (veja, estou usando como diário), então vou ter que deixar o nix aí.
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# nix Pra instalar o [neuron](797984e3.md) fui forçado a baixar e instalar o [nix](https://nixos.org/download.html). Não consegui me lembrar por que não estava usando até hoje aquele maravilhoso sistema de instalar pacotes desde a primeira vez que tentei, anos atrás. Que sofrimento pra fazer funcionar com o `fish`, mas até que bem menos sofrimento que da outra vez. Tive que instalar um tal de `fish-foreign-environment` (usando o próprio nix!, já que a outra opção era o `oh-my-fish` ou qualquer outra porcaria dessas) e aí usá-lo para aplicar as definições de shell para bash direto no `fish`. E aí lembrei também que o `/nix/store` fica cheio demais, o negócio instala tudo que existe neste mundo a partir do zero. É só para computadores muito ricos, mas vamos ver como vai ser. Estou gostando do neuron (veja, estou usando como diário), então vou ter que deixar o nix aí. @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# O Bitcoin como um sistema social humano Afinal de contas, o que é o Bitcoin? Não vou responder a essa pergunta explicando o que é uma "blockchain" ou coisa que o valha, como todos fazem muito pessimamente. [A melhor explicação em português que eu já vi está aqui](nostr:naddr1qqrky6t5vdhkjmspz9mhxue69uhkv6tpw34xze3wvdhk6q3q80cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsxpqqqp65wp3k3fu), mas mesmo assim qualquer explicação jamais será definitiva. A explicação apenas do protocolo, do que faz um programa `bitcoind` sendo executado em um computador e como ele se comunica com outros em outros computadores, e os incentivos que estão em jogo para garantir com razoável probabilidade que se chegará a um consenso sobre quem é dono de qual parte de qual transação, apesar de não ser complicada demais, exigirá do iniciante que seja compreendida muitas vezes antes que ele se possa se sentir confortável para dizer que entende um pouco. E essa parte _técnica_, apesar de ter sido o insight fundamental que gerou o evento miraculoso chamado Bitcoin, não é a parte mais importante, hoje. Se fosse, várias dessas outras moedas seriam concorrentes do Bitcoin, mas não são, e jamais poderão ser, porque elas não estão nem próximas de ter os outros elementos que compõem o Bitcoin. São eles: 1. A estrutura O Bitcoin é um sistema composto de partes independentes. Existem programadores que trabalham no protocolo e aplicações, e dia após dia novos programadores chegam e outros saem, e eles trabalham às vezes em conjunto, às vezes sem que um se dê conta do outro, às vezes por conta própria, às vezes pagos por empresas interessadas. Existem os usuários que realizam validação completa, isto é, estão rodando algum programa do Bitcoin e contribuindo para a difusão dos blocos, das transações, rejeitando usuários malignos e evitando ataques de mineradores mal-intencionados. Existem os poupadores, acumuladores ou os proprietários de bitcoins, que conhecem as possibilidades que o mundo reserva para o Bitcoin, esperam o dia em que o padrão-Bitcoin será uma realidade mundial e por isso mesmo atributem aos seus bitcoins valores muito mais altos do que os preços atuais de mercado, agarrando-se a eles. Especuladores de "criptomoedas" não fazem parte desse sistema, nem tampouco empresas que [aceitam pagamento](https://bitpay.com/) em bitcoins para imediatamente venderem tudo em troca de dinheiro estatal, e menos ainda [gente que usa bitcoins](https://www.investimentobitcoin.com/) e [a própria marca Bitcoin](https://www.xdex.com.br/) para aplicar seus golpes e coisas parecidas. 2. A cultura Mencionei que há empresas que pagam programadores para trabalharem no código aberto do BitcoinCore ou de outros programas relacionados à rede Bitcoin -- ou mesmo em aplicações não necessariamente ligadas à camada fundamental do protocolo. Nenhuma dessas empresas interessadas, porém, controla o Bitcoin, e isso é o elemento principal da cultura do Bitcoin. O propósito do Bitcoin sempre foi ser uma rede aberta, sem chefes, sem política envolvida, sem necessidade de pedir autorização para participar. O fato do próprio Satoshi Nakamoto ter voluntariamente desaparecido das discussões foi fundamental para que o Bitcoin não fosse visto como um sistema dependente dele ou que ele fosse entendido como o chefe. Em outras "criptomoedas" nada disso aconteceu. O chefe supremo do Ethereum continua por aí mandando e desmandando e inventando novos elementos para o protocolo que são automaticamente aceitos por toda a comunidade, o mesmo vale para o Zcash, EOS, Ripple, Litecoin e até mesmo para o Bitcoin Cash. Pior ainda: Satoshi Nakamoto saiu sem nenhum dinheiro, nunca mexeu nos milhares de bitcoins que ele gerou nos primeiros blocos -- enquanto os líderes dessas porcarias supramencionadas cobraram uma fortuna pelo direito de uso dos seus primeiros usuários ou estão aí a até hoje receber dividendos. Tudo isso e mais outras coisas -- a mentalidade anti-estatal e entusiasta de sistemas p2p abertos dos membros mais proeminentes da comunidade, por exemplo -- faz com que um ar de liberdade e suspeito de tentativas de centralização da moeda sejam percebidos e execrados. 3. A história A noção de que o Bitcoin não pode ser controlado por ninguém passou em 2017 por [dois testes](https://www.forbes.com/sites/ktorpey/2019/04/23/this-key-part-of-bitcoins-history-is-what-separates-it-from-competitors/#49869b41ae5e) e saiu deles muito reforçada: o primeiro foi a divisão entre Bitcoin (BTC) e Bitcoin Cash (BCH), uma obra de engenharia social que teve um sucesso mediano em roubar parte da marca e dos usuários do verdadeiro Bitcoin e depois a tentativa de tomada por completo do Bitcoin promovida por mais ou menos as mesmas partes interessadas chamada SegWit2x, que fracassou por completo, mas não sem antes atrapalhar e difundir mentiras para todos os lados. Esses dois fracassos provaram que o Bitcoin, mesmo sendo uma comunidade desorganizada, sem líderes claros, está imune à [captura por grupos interessados](https://en.wikipedia.org/wiki/Regulatory_capture), o que é mais um milagre -- ou, como dizem, um [ponto de Schelling](https://en.wikipedia.org/wiki/Focal_point_(game_theory)). Esse período crucial na história do Bitcoin fez com ficasse claro que _hard-forks_ são essencialmente incompatíveis com a natureza do protocolo, de modo que no futuro não haverá a possibilidade de uma sugestão como a de imprimir mais bitcoins do que o que estava programado sejam levadas a sério (mas, claro, sempre há a possibilidade da cultura toda se perder, as pessoas esquecerem a história e o Bitcoin ser cooptado, eis a importância da auto-educação e da difusão desses princípios).
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# O Bitcoin como um sistema social humano Afinal de contas, o que é o Bitcoin? Não vou responder a essa pergunta explicando o que é uma "blockchain" ou coisa que o valha, como todos fazem muito pessimamente. [A melhor explicação em português que eu já vi está aqui](nostr:naddr1qqrky6t5vdhkjmspz9mhxue69uhkv6tpw34xze3wvdhk6q3q80cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsxpqqqp65wp3k3fu), mas mesmo assim qualquer explicação jamais será definitiva. A explicação apenas do protocolo, do que faz um programa `bitcoind` sendo executado em um computador e como ele se comunica com outros em outros computadores, e os incentivos que estão em jogo para garantir com razoável probabilidade que se chegará a um consenso sobre quem é dono de qual parte de qual transação, apesar de não ser complicada demais, exigirá do iniciante que seja compreendida muitas vezes antes que ele se possa se sentir confortável para dizer que entende um pouco. E essa parte _técnica_, apesar de ter sido o insight fundamental que gerou o evento miraculoso chamado Bitcoin, não é a parte mais importante, hoje. Se fosse, várias dessas outras moedas seriam concorrentes do Bitcoin, mas não são, e jamais poderão ser, porque elas não estão nem próximas de ter os outros elementos que compõem o Bitcoin. São eles: 1. A estrutura O Bitcoin é um sistema composto de partes independentes. Existem programadores que trabalham no protocolo e aplicações, e dia após dia novos programadores chegam e outros saem, e eles trabalham às vezes em conjunto, às vezes sem que um se dê conta do outro, às vezes por conta própria, às vezes pagos por empresas interessadas. Existem os usuários que realizam validação completa, isto é, estão rodando algum programa do Bitcoin e contribuindo para a difusão dos blocos, das transações, rejeitando usuários malignos e evitando ataques de mineradores mal-intencionados. Existem os poupadores, acumuladores ou os proprietários de bitcoins, que conhecem as possibilidades que o mundo reserva para o Bitcoin, esperam o dia em que o padrão-Bitcoin será uma realidade mundial e por isso mesmo atributem aos seus bitcoins valores muito mais altos do que os preços atuais de mercado, agarrando-se a eles. Especuladores de "criptomoedas" não fazem parte desse sistema, nem tampouco empresas que [aceitam pagamento](https://bitpay.com/) em bitcoins para imediatamente venderem tudo em troca de dinheiro estatal, e menos ainda [gente que usa bitcoins](https://www.investimentobitcoin.com/) e [a própria marca Bitcoin](https://www.xdex.com.br/) para aplicar seus golpes e coisas parecidas. 2. A cultura Mencionei que há empresas que pagam programadores para trabalharem no código aberto do BitcoinCore ou de outros programas relacionados à rede Bitcoin -- ou mesmo em aplicações não necessariamente ligadas à camada fundamental do protocolo. Nenhuma dessas empresas interessadas, porém, controla o Bitcoin, e isso é o elemento principal da cultura do Bitcoin. O propósito do Bitcoin sempre foi ser uma rede aberta, sem chefes, sem política envolvida, sem necessidade de pedir autorização para participar. O fato do próprio Satoshi Nakamoto ter voluntariamente desaparecido das discussões foi fundamental para que o Bitcoin não fosse visto como um sistema dependente dele ou que ele fosse entendido como o chefe. Em outras "criptomoedas" nada disso aconteceu. O chefe supremo do Ethereum continua por aí mandando e desmandando e inventando novos elementos para o protocolo que são automaticamente aceitos por toda a comunidade, o mesmo vale para o Zcash, EOS, Ripple, Litecoin e até mesmo para o Bitcoin Cash. Pior ainda: Satoshi Nakamoto saiu sem nenhum dinheiro, nunca mexeu nos milhares de bitcoins que ele gerou nos primeiros blocos -- enquanto os líderes dessas porcarias supramencionadas cobraram uma fortuna pelo direito de uso dos seus primeiros usuários ou estão aí a até hoje receber dividendos. Tudo isso e mais outras coisas -- a mentalidade anti-estatal e entusiasta de sistemas p2p abertos dos membros mais proeminentes da comunidade, por exemplo -- faz com que um ar de liberdade e suspeito de tentativas de centralização da moeda sejam percebidos e execrados. 3. A história A noção de que o Bitcoin não pode ser controlado por ninguém passou em 2017 por [dois testes](https://www.forbes.com/sites/ktorpey/2019/04/23/this-key-part-of-bitcoins-history-is-what-separates-it-from-competitors/#49869b41ae5e) e saiu deles muito reforçada: o primeiro foi a divisão entre Bitcoin (BTC) e Bitcoin Cash (BCH), uma obra de engenharia social que teve um sucesso mediano em roubar parte da marca e dos usuários do verdadeiro Bitcoin e depois a tentativa de tomada por completo do Bitcoin promovida por mais ou menos as mesmas partes interessadas chamada SegWit2x, que fracassou por completo, mas não sem antes atrapalhar e difundir mentiras para todos os lados. Esses dois fracassos provaram que o Bitcoin, mesmo sendo uma comunidade desorganizada, sem líderes claros, está imune à [captura por grupos interessados](https://en.wikipedia.org/wiki/Regulatory_capture), o que é mais um milagre -- ou, como dizem, um [ponto de Schelling](https://en.wikipedia.org/wiki/Focal_point_(game_theory)). Esse período crucial na história do Bitcoin fez com ficasse claro que _hard-forks_ são essencialmente incompatíveis com a natureza do protocolo, de modo que no futuro não haverá a possibilidade de uma sugestão como a de imprimir mais bitcoins do que o que estava programado sejam levadas a sério (mas, claro, sempre há a possibilidade da cultura toda se perder, as pessoas esquecerem a história e o Bitcoin ser cooptado, eis a importância da auto-educação e da difusão desses princípios). @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# O caso da Grêmio TV enquanto vinha se conduzindo pela plataforma superior daquela arena que se pensava totalmente preenchida por adeptos da famosa equipe do Grêmio de Porto Alegre, viu-se, como por obra de algum nigromante - dos muitos que existem e estão a todo momento a fazer más obras e a colocar-se no caminhos dos que procuram, se não fazer o bem acima de todas as coisas, a pelo menos não fazer o mal no curso da realização dos seus interesses -, o discretíssimo jornalista a ser xingado e moído em palavras por uma horda de malandrinos a cinco ou seis passos dele surgida que cantavam e moviam seus braços em movimentos que não se pode classificar senão como bárbaros, e assim cantavam: Grêmio TV pior que o SBT !
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# O caso da Grêmio TV enquanto vinha se conduzindo pela plataforma superior daquela arena que se pensava totalmente preenchida por adeptos da famosa equipe do Grêmio de Porto Alegre, viu-se, como por obra de algum nigromante - dos muitos que existem e estão a todo momento a fazer más obras e a colocar-se no caminhos dos que procuram, se não fazer o bem acima de todas as coisas, a pelo menos não fazer o mal no curso da realização dos seus interesses -, o discretíssimo jornalista a ser xingado e moído em palavras por uma horda de malandrinos a cinco ou seis passos dele surgida que cantavam e moviam seus braços em movimentos que não se pode classificar senão como bárbaros, e assim cantavam: Grêmio TV pior que o SBT ! @ 3bf0c63f:aefa459d
2024-01-14 13:55:28# My stupid introduction to Haskell While I was writing my first small program on Haskell (really simple, but functional webapp) in December 2017 I only knew vaguely what was the style of things, some basic notions about functions, pure functions and so on (I've read about a third of [LYAH](http://learnyouahaskell.com/chapters)). An enourmous amount of questions began to appear in my head while I read tutorials and documentation. Here I present some of the questions and the insights I got that solved them. Technically, they may be wrong, but they helped me advance in the matter, so I'm writing them down while I still can -- If I keep working with Haskell I'll probably get to know more and so my new insights will replace the previous ones, and the new ones won't be useful for total begginers anymore. --- Here we go: - **Why do modules have odd names?** - modules are the things you import, like `Data.Time.Clock` or `Web.Scotty`. - packages are the things you install, like 'time' or 'scotty' - packages can contain any number of modules they like - a module is just a collection of functions - a package is just a collection of modules - a package is just name you choose to associate your collection of modules with when you're publishing it to Hackage or whatever - the module names you choose when you're writing a package can be anything, and these are the names people will have to `import` when they want to use you functions - if you're from Javascript, Python or anything similar, you'll expect to be importing/writing the name of the package directly in your code, but in Haskell you'll actually be writing the name of the module, which may have nothing to do with the name of the package - people choose things that make sense, like for `aeson` instead of `import Aeson` you'll be doing `import Data.Aeson`, `import Data.Aeson.Types` etc. why the `Data`? because they thought it would be nice. dealing with JSON is a form of dealing with data, so be it. - you just have to check the package documentation to see which modules it exposes. - **What is `data User = User { name :: Text }`?** - a data type definition. means you'll have a function `User` that will take a Text parameter and output a `User` record or something like that. - you can also have `Animal = Giraffe { color :: Text } | Human { name :: Text }`, so you'll have two functions, Giraffe and Human, each can take a different set of parameters, but they will both yield an Animal. - then, in the functions that take an Animal parameter you must typematch to see if the animal is a giraffe or a human. - **What is a monad?** - a monad is a context, an environment. - when you're in the context of a monad you can write imperative code. - you do that when you use the keyword `do`. - in the context of a monad, all values are prefixed by the monad type, - thus, in the `IO` monad all `Text` is `IO Text` and so on. - some monads have a relationship with others, so values from that monad can be turned into values from another monad and passed between context easily. - for exampĺe, [scotty](https://www.stackage.org/haddock/lts-9.18/scotty-0.11.0/Web-Scotty.html)'s `ActionM` and `IO`. `ActionM` is just a subtype of `IO` or something like that. - when you write imperative code inside a monad you can do assignments like `varname <- func x y` - in these situations some transformation is done by the `<-`, I believe it is that the pure value returned by `func` is being transformed into a monad value. so if `func` returns `Text`, now varname is of type `IO Text` (if we're in the IO monad). - so it will not work (and it can be confusing) if you try to concatenate functions like `varname <- transform $ func x y`, but you can somehow do - `varname <- func x y` - `othervarname <- transform varname` - or you can do other fancy things you'll get familiar with later, like `varname <- fmap transform $ func x y` - why? I don't know. - **How do I deal with Maybe, Either or other crazy stuff?** "ok, I understand what is a Maybe: it is a value that could be something or nothing. but how do I use that in my program?" - you don't! you turn it into other thing. for example, you use [fromMaybe](http://hackage.haskell.org/package/base-4.10.1.0/docs/Data-Maybe.html#v:fromMaybe), a function that takes a default value and that's it. if your `Maybe` is `Just x` you get `x`, if it is `Nothing` you get the default value. - using only that function you can already do whatever there is to be done with Maybes. - you can also manipulate the values inside the `Maybe`, for example: - if you have a `Maybe Person` and `Person` has a `name` which is `Text`, you can apply a function that turns `Maybe Person` into `Maybe Text` AND ONLY THEN you apply the default value (which would be something like the `"unnamed"`) and take the name from inside the `Maybe`. - basically these things (`Maybe`, `Either`, `IO` also!) are just tags. they tag the value, and you can do things with the values inside them, or you can remove the values. - besides the example above with Maybes and the `fromMaybe` function, you can also remove the values by using `case` -- for example: - `case x of` - `Left error -> error` - `Right success -> success` - `case y of` - `Nothing -> "nothing!"` - `Just value -> value` - (in some cases I believe you can't remove the values, but in these cases you'll also don't need to) - for example, for values tagged with the IO, you can't remove the IO and turn these values into pure values, but you don't need that, you can just take the value from the outside world, so it's a IO Text, apply functions that modify that value inside IO, then output the result to the user -- this is enough to make a complete program, any complete program. - **JSON and interfaces (or instances?)** - using [Aeson](https://hackage.haskell.org/package/aeson-1.2.3.0/docs/Data-Aeson.html) is easy, you just have to implement the `ToJSON` and `FromJSON` interfaces. - "interface" is not the correct name, but I don't care. - `ToJSON`, for example, requires a function named `toJSON`, so you do - `instance ToJSON YourType where` - `toJSON (YourType your type values) = object []` ... etc. - I believe lots of things require interface implementation like this and it can be confusing, but once you know the mystery of implementing functions for interfaces everything is solved. - `FromJSON` is a little less intuitive at the beggining, and I don't know if I did it correctly, but it is working here. Anyway, if you're trying to do that, I can only tell you to follow the types, copy examples from other places on the internet and don't care about the meaning of symbols. ## See also * [Haskell Monoids](nostr:naddr1qqyrzcmrvcmrqwtpqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cktq992)
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28# My stupid introduction to Haskell While I was writing my first small program on Haskell (really simple, but functional webapp) in December 2017 I only knew vaguely what was the style of things, some basic notions about functions, pure functions and so on (I've read about a third of [LYAH](http://learnyouahaskell.com/chapters)). An enourmous amount of questions began to appear in my head while I read tutorials and documentation. Here I present some of the questions and the insights I got that solved them. Technically, they may be wrong, but they helped me advance in the matter, so I'm writing them down while I still can -- If I keep working with Haskell I'll probably get to know more and so my new insights will replace the previous ones, and the new ones won't be useful for total begginers anymore. --- Here we go: - **Why do modules have odd names?** - modules are the things you import, like `Data.Time.Clock` or `Web.Scotty`. - packages are the things you install, like 'time' or 'scotty' - packages can contain any number of modules they like - a module is just a collection of functions - a package is just a collection of modules - a package is just name you choose to associate your collection of modules with when you're publishing it to Hackage or whatever - the module names you choose when you're writing a package can be anything, and these are the names people will have to `import` when they want to use you functions - if you're from Javascript, Python or anything similar, you'll expect to be importing/writing the name of the package directly in your code, but in Haskell you'll actually be writing the name of the module, which may have nothing to do with the name of the package - people choose things that make sense, like for `aeson` instead of `import Aeson` you'll be doing `import Data.Aeson`, `import Data.Aeson.Types` etc. why the `Data`? because they thought it would be nice. dealing with JSON is a form of dealing with data, so be it. - you just have to check the package documentation to see which modules it exposes. - **What is `data User = User { name :: Text }`?** - a data type definition. means you'll have a function `User` that will take a Text parameter and output a `User` record or something like that. - you can also have `Animal = Giraffe { color :: Text } | Human { name :: Text }`, so you'll have two functions, Giraffe and Human, each can take a different set of parameters, but they will both yield an Animal. - then, in the functions that take an Animal parameter you must typematch to see if the animal is a giraffe or a human. - **What is a monad?** - a monad is a context, an environment. - when you're in the context of a monad you can write imperative code. - you do that when you use the keyword `do`. - in the context of a monad, all values are prefixed by the monad type, - thus, in the `IO` monad all `Text` is `IO Text` and so on. - some monads have a relationship with others, so values from that monad can be turned into values from another monad and passed between context easily. - for exampĺe, [scotty](https://www.stackage.org/haddock/lts-9.18/scotty-0.11.0/Web-Scotty.html)'s `ActionM` and `IO`. `ActionM` is just a subtype of `IO` or something like that. - when you write imperative code inside a monad you can do assignments like `varname <- func x y` - in these situations some transformation is done by the `<-`, I believe it is that the pure value returned by `func` is being transformed into a monad value. so if `func` returns `Text`, now varname is of type `IO Text` (if we're in the IO monad). - so it will not work (and it can be confusing) if you try to concatenate functions like `varname <- transform $ func x y`, but you can somehow do - `varname <- func x y` - `othervarname <- transform varname` - or you can do other fancy things you'll get familiar with later, like `varname <- fmap transform $ func x y` - why? I don't know. - **How do I deal with Maybe, Either or other crazy stuff?** "ok, I understand what is a Maybe: it is a value that could be something or nothing. but how do I use that in my program?" - you don't! you turn it into other thing. for example, you use [fromMaybe](http://hackage.haskell.org/package/base-4.10.1.0/docs/Data-Maybe.html#v:fromMaybe), a function that takes a default value and that's it. if your `Maybe` is `Just x` you get `x`, if it is `Nothing` you get the default value. - using only that function you can already do whatever there is to be done with Maybes. - you can also manipulate the values inside the `Maybe`, for example: - if you have a `Maybe Person` and `Person` has a `name` which is `Text`, you can apply a function that turns `Maybe Person` into `Maybe Text` AND ONLY THEN you apply the default value (which would be something like the `"unnamed"`) and take the name from inside the `Maybe`. - basically these things (`Maybe`, `Either`, `IO` also!) are just tags. they tag the value, and you can do things with the values inside them, or you can remove the values. - besides the example above with Maybes and the `fromMaybe` function, you can also remove the values by using `case` -- for example: - `case x of` - `Left error -> error` - `Right success -> success` - `case y of` - `Nothing -> "nothing!"` - `Just value -> value` - (in some cases I believe you can't remove the values, but in these cases you'll also don't need to) - for example, for values tagged with the IO, you can't remove the IO and turn these values into pure values, but you don't need that, you can just take the value from the outside world, so it's a IO Text, apply functions that modify that value inside IO, then output the result to the user -- this is enough to make a complete program, any complete program. - **JSON and interfaces (or instances?)** - using [Aeson](https://hackage.haskell.org/package/aeson-1.2.3.0/docs/Data-Aeson.html) is easy, you just have to implement the `ToJSON` and `FromJSON` interfaces. - "interface" is not the correct name, but I don't care. - `ToJSON`, for example, requires a function named `toJSON`, so you do - `instance ToJSON YourType where` - `toJSON (YourType your type values) = object []` ... etc. - I believe lots of things require interface implementation like this and it can be confusing, but once you know the mystery of implementing functions for interfaces everything is solved. - `FromJSON` is a little less intuitive at the beggining, and I don't know if I did it correctly, but it is working here. Anyway, if you're trying to do that, I can only tell you to follow the types, copy examples from other places on the internet and don't care about the meaning of symbols. ## See also * [Haskell Monoids](nostr:naddr1qqyrzcmrvcmrqwtpqyghwumn8ghj7enfv96x5ctx9e3k7mgzyqalp33lewf5vdq847t6te0wvnags0gs0mu72kz8938tn24wlfze6qcyqqq823cktq992)