-

@ 5e5fc143:393d5a2c
2024-11-19 10:20:25
Now test old reliable front end
Stay tuned more later
Keeping this as template long note for debugging in future as come across few NIP-33 post edit issues
-

@ af9c48b7:a3f7aaf4
2024-11-18 20:26:07
## Chef's notes
This simple, easy, no bake desert will surely be the it at you next family gathering. You can keep it a secret or share it with the crowd that this is a healthy alternative to normal pie. I think everyone will be amazed at how good it really is.
## Details
- ⏲️ Prep time: 30
- 🍳 Cook time: 0
- 🍽️ Servings: 8
## Ingredients
- 1/3 cup of Heavy Cream- 0g sugar, 5.5g carbohydrates
- 3/4 cup of Half and Half- 6g sugar, 3g carbohydrates
- 4oz Sugar Free Cool Whip (1/2 small container) - 0g sugar, 37.5g carbohydrates
- 1.5oz box (small box) of Sugar Free Instant Chocolate Pudding- 0g sugar, 32g carbohydrates
- 1 Pecan Pie Crust- 24g sugar, 72g carbohydrates
## Directions
1. The total pie has 30g of sugar and 149.50g of carboydrates. So if you cut the pie into 8 equal slices, that would come to 3.75g of sugar and 18.69g carbohydrates per slice. If you decided to not eat the crust, your sugar intake would be .75 gram per slice and the carborytrates would be 9.69g per slice. Based on your objective, you could use only heavy whipping cream and no half and half to further reduce your sugar intake.
2. Mix all wet ingredients and the instant pudding until thoroughly mixed and a consistent color has been achieved. The heavy whipping cream causes the mixture to thicken the more you mix it. So, I’d recommend using an electric mixer. Once you are satisfied with the color, start mixing in the whipping cream until it has a consistent “chocolate” color thorough. Once your satisfied with the color, spoon the mixture into the pie crust, smooth the top to your liking, and then refrigerate for one hour before serving.
-

@ a39d19ec:3d88f61e
2024-11-17 10:48:56
This week's functional 3d print is the "Dino Clip".

## Dino Clip
I printed it some years ago for my son, so he would have his own clip for cereal bags.
Now it is used to hold a bag of dog food close.
The design by "Sneaks" is a so called "print in place". This means that the whole clip with moving parts is printed in one part, without the need for assembly after the print.

The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at [Printables](https://www.printables.com/model/64493-dino-clip-mechanical-cam-chip-clip-print-in-place)
-

@ fd208ee8:0fd927c1
2024-11-17 09:14:56
You don't understand how insidious open-borders propaganda is, until you realize that _it's an attempt to remove all differentiating traits from humans_. They call this "strengthening individuality by removing nationality" (hello, newspeak), but what makes humans individual is their particular collection of traits, and nationality (and ethnicity, religion, etc. -- nationality is just the first domino they want to topple) is one of those.

Humans are not blank slates. Like DNA or physiognomy, our personalities are differing jumbles of cultural "letters". Each person selects consciously and subconsciously from amongst these letters, adding to or rejecting them, amplifying or suppressing them, twisting or combining them, building on top of them... and that's what makes you into You.
Open borders is an attempt to reduce the number of cultural letters you can build your "You" out of. If you take away the word "German", I am not liberated. There is simply one less adjective, with which I can describe myself. You have merely eradicated information, crippled language, and reduced my choices. I can then no longer define myself according to "German things", but I can also no longer define myself in opposition to German things.
## Enter the Borg

We are easier to control and brainwash and persecute, if we are centralized and homogenized. As if the entire world were one, big prison and we were all forced to undergo the same education, wear the same clothes, follow the same rules, eat the same foods, enjoy the same entertainment, live the same lifestyle, share the same diseases and cures, enjoy the same lockdowns, join in the same cancel culture, fight the same wars.
That is what globalization brings. That is the end game of Open Borders:
* No more cultural evolution or revolution.
* Genes, but no memes.
* You can go everywhere, but everywhere is the same, so you just stay home.
* You can meet people from all over, but they are all the same, so you just don't bother.
* One mass of humanity, that can be easily molded and manipulated.
-

@ 13351007:eccd002a
2024-11-13 16:34:01
[{"_id":"5478974e-5e9b-4ccc-8cee-8485f60838ef","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":202.86468,"amountCurrency":"xmr","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:34:01.270Z"},{"_id":"5478974e-5e9b-4ccc-8cee-8485f60838ef","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"5478974e-5e9b-4ccc-8cee-8485f60838ef","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":202.86468,"amountCurrency":"xmr","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:34:01.270Z"}]
-

@ 13351007:eccd002a
2024-11-13 16:33:01
[{"_id":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.03,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:33:01.332Z"},{"_id":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.03,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:33:01.332Z"}]
-

@ 13351007:eccd002a
2024-11-13 16:32:01
[{"_id":"a740e2cb-8940-4d1b-bf4c-271de778bd77","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.02,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:32:01.342Z"},{"_id":"a740e2cb-8940-4d1b-bf4c-271de778bd77","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"a740e2cb-8940-4d1b-bf4c-271de778bd77","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.02,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:32:01.342Z"}]
-

@ 13351007:eccd002a
2024-11-13 16:31:10
[{"_id":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.01,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:31:10.741Z"},{"_id":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.01,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:31:10.741Z"}]
-

@ 13351007:eccd002a
2024-11-13 14:50:53
[{"_id":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T14:50:53.706Z"},{"_id":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T14:50:53.706Z"}]
-

@ 13351007:eccd002a
2024-11-13 09:17:38
[{"_id":"f61999d4-6dd5-4593-9798-17980ecebd22","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100.02,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T09:17:38.105Z"},{"_id":"f61999d4-6dd5-4593-9798-17980ecebd22","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"f61999d4-6dd5-4593-9798-17980ecebd22","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100.02,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T09:17:38.105Z"}]
-

@ 13351007:eccd002a
2024-11-13 08:02:18
[{"_id":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":102,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T08:02:18.346Z"},{"_id":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":102,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T08:02:18.346Z"}]
-

@ 13351007:eccd002a
2024-11-13 07:54:13
[{"_id":"b99131ca-10fb-48fd-be00-04aee70efd55","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.400Z"},{"_id":"b99131ca-10fb-48fd-be00-04aee70efd55","tradingPartner":"liam","tradeId":"b99131ca-10fb-48fd-be00-04aee70efd55","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.400Z"}]
-

@ 13351007:eccd002a
2024-11-13 07:54:13
[{"_id":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":101,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.286Z"},{"_id":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","tradingPartner":"liam","tradeId":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":101,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.286Z"}]
-

@ 13351007:eccd002a
2024-11-13 06:54:35
{"_id":"d12af7f8-9fad-4718-85d2-71de3e1ab22f","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":1,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.527Z"}
-

@ 13351007:eccd002a
2024-11-13 06:54:35
{"_id":"45961f60-af28-49a7-8285-39d46a04ae04","tradingPartner":"liam","adId":"10df86b1-657c-4065-b5c8-d6f6bbe64a7b","adPublisher":"f462d21e10163eb0a403aec6b93ac57ec2f1b9455473e99304f571a51390b6b1","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":170.27,"amount":1.5,"amountCurrency":"fiat","paymentMethodCode":"VENMO","currencyCode":"USD","country":"United Kingdom","countryCode":"GB","paymentMethodDetail":"best rates really","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.127Z"}
-

@ 13351007:eccd002a
2024-11-13 06:54:35
{"_id":"79c3b4de-fb00-40e6-82b4-9c8474d90c43","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":1.6,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.210Z"}
-

@ 13351007:eccd002a
2024-11-13 06:54:35
{"_id":"6189965d-885f-44a5-8283-236809f90bb4","tradingPartner":"liam","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":2,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.193Z"}
-

@ 13351007:eccd002a
2024-11-13 06:54:34
{"_id":"fad63d53-f555-429e-916a-d2ea8968552d","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":20,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:34.754Z"}
-

@ 13351007:eccd002a
2024-11-12 17:32:12
just testing with p tag
-

@ 13351007:eccd002a
2024-11-12 16:33:39
just testing with p tag
-

@ 13351007:eccd002a
2024-11-12 15:44:07
just testing
-

@ 6be5cc06:5259daf0
2024-11-12 03:11:11
### Primeiramente, o que é mempool?
Abreviação de memory pool (ou *"pool de memória"*) a mempool é uma espécie de fila onde as transações de Bitcoin ficam temporariamente armazenadas antes de serem confirmadas e incluídas em um bloco na blockchain.
Quando você realiza uma transação em uma rede blockchain, essa transação precisa ser validada e confirmada pelos mineradores (ou validadores). Porém, ela não é processada instantaneamente. Primeiro, ela vai para a mempool, onde aguarda até que um minerador a selecione para incluir no próximo bloco.
É assim:
* Você envia uma transação, ela é transmitida para a rede e vai parar na mempool de vários nós (computadores) que suportam a rede blockchain.
* As transações na mempool são organizadas pela taxa de transação que foi anexada. Quanto maior a taxa, mais rápido os mineradores tendem a escolher essa transação para incluí-la em um bloco, pois isso aumenta os ganhos deles.
* Os mineradores pegam as transações da mempool, criam um bloco com elas e, ao minerar (confirmar) esse bloco, as transações saem da mempool e entram na blockchain.
Aqui irei usar o site [mempool.emzy.de](https://mempool.emzy.de/) como referência, mas é importante entender que sites de mempool são representações visuais da mempool de um nó específico e não *a mempool do Bitcoin* em si. Ela não é centralizada, cada nó da rede mantém a sua própria versão da mempool. Assim, ela pode variar de um nó para outro. Esses sites ajudam a visualizar dados sobre transações e taxas.
É uma boa prática usar **VPN** ou **Tor** ao acessar tais sites se você estiver verificando uma transação específica sua, pois sua privacidade pode ficar comprometida se o site registrar esses dados. Se você estiver repetidamente acessando-o para monitorar a confirmação de uma transação, alguém pode conseguir correlacionar o endereço IP com essa atividade e revelar uma conexão indireta com o endereço da transação.
Dito isso...
### Como interpretar a mempool?
Vamos dividir isso em partes para fins didáticos.
---
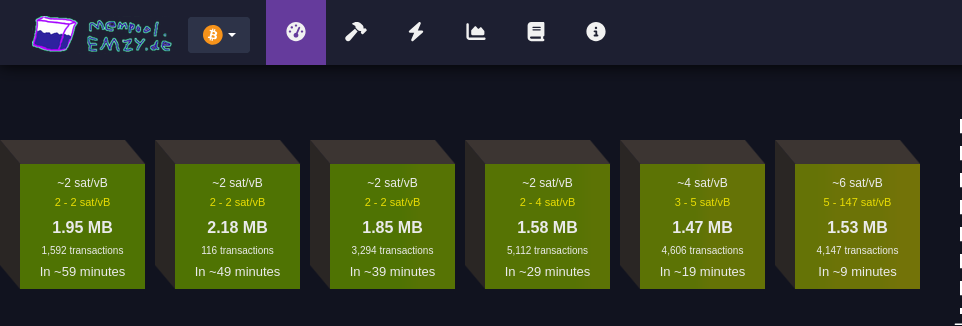
#### Faixa de taxas
Cada bloco verde representa uma faixa de taxa medida em satoshis por vByte (sats/vB).
Essa unidade de medida representa o valor pago por byte ocupado pela transação.
Quanto maior a taxa paga por uma transação, mais rápido ela tende a ser confirmada.
Quanto maior a transação em bytes, mais você precisa pagar para que ela seja confirmada.
Cada transação Bitcoin consiste em *entradas* e *saídas* (*inputs* e *outputs*):
* **Entradas** são referências a transações anteriores que estão sendo gastas, e cada entrada inclui informações como o endereço de origem, a assinatura (que valida a transação e pode variar de tamanho dependendo da complexidade da chave e do método de assinatura utilizado (como SegWit, que é mais eficiente). Quanto mais complexa a assinatura, maior será o tamanho em bytes) e outros dados. Quanto mais entradas uma transação tiver, maior será seu tamanho.
* **Saídas** representam o destino do Bitcoin, e quanto mais saídas, maior será o tamanho da transação. Embora as saídas ocupem menos espaço em bytes do que as entradas.
Ex.:
* ~4 sat/vB: Indica uma taxa média. Significa que, em média, as transações estão sendo processadas a 4 satoshis por vByte;
* 3-5 sat/vB: Isso significa que as transações estão sendo processadas com uma taxa entre 3 e 5 satoshis por vByte.
#### MB
Simplesmente o tamanho do bloco medido em megabytes :)
#### Número de transações
Essa seção informa quantas transações estão aguardando confirmação para cada faixa de taxa (bloco). Quanto maior o número de transações, maior a demanda pela faixa de taxa especificada.
#### Tempo estimado para confirmação
Aqui é mostrado o tempo médio de espera para transações que pagam taxas dentro da faixa especificada. Se você pagar uma taxa maior, a transação será confirmada mais rapidamente; uma taxa menor significa que a transação pode levar mais tempo para ser confirmada, especialmente se a rede estiver congestionada.
---
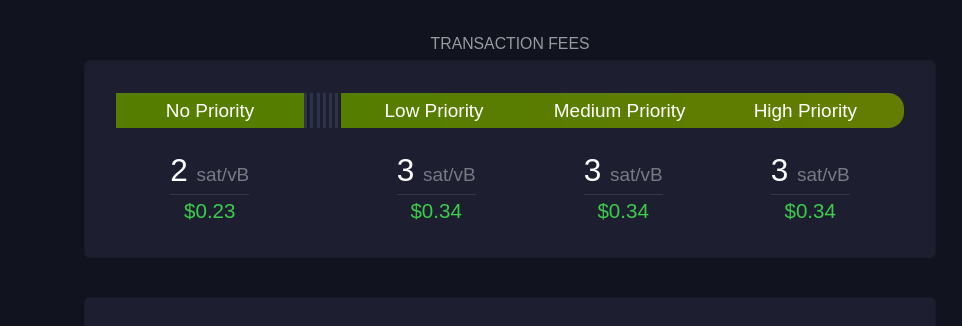
Esta seção mostra sugestões de taxa em diferentes níveis de prioridade para os usuários:
#### Sem Prioridade
Exibe a taxa mínima necessária para transações que não precisam de confirmação rápida.
#### Prioridade Baixa
Sugestão de taxa para transações que podem esperar um tempo moderado, com expectativa de confirmação em um ou dois blocos.
#### Prioridade Média e Alta
São as faixas de taxa recomendadas para quem precisa que a transação seja confirmada rapidamente. "Prioridade Alta" paga uma taxa maior, garantindo que a transação seja incluída no próximo bloco.
---
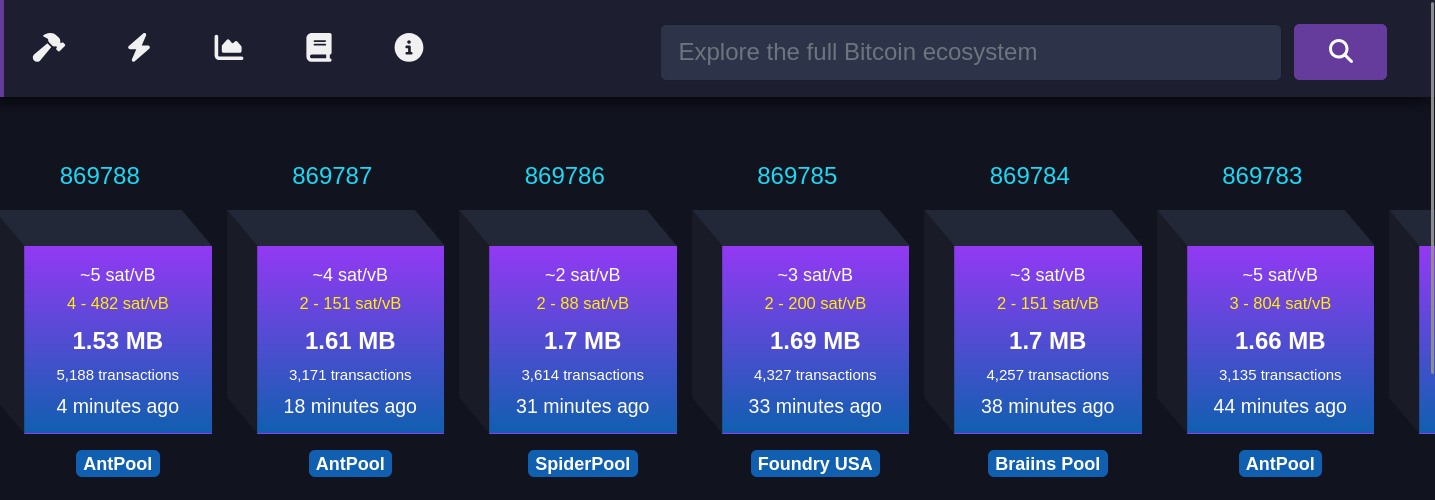
Cada bloco roxo representa um bloco recém-minerado. As informações mostradas incluem:
#### Taxa média paga
Refere-se à taxa média em satoshis/vB paga por todas as transações incluídas em um bloco recém-minerado. Isso reflete o valor médio que os usuários estão dispostos a pagar para que suas transações sejam confirmadas rapidamente.
#### Número de transações
Este número indica quantas transações foram processadas no bloco minerado. O tamanho do bloco é limitado, então, quanto maior o número de transações, menor será o espaço disponível para novas transações, o que pode influenciar as taxas de transação.
#### Tempo desde a mineração
Esta métrica informa quanto tempo se passou desde que o bloco foi minerado e adicionado à blockchain.
#### Pool de mineração
Exibe o nome do pool de mineração que minerou o bloco, como AntPool. Grandes pools de mineração têm mais chances de minerar blocos regularmente devido ao alto hashrate (medida da capacidade computacional utilizada pelos mineradores) que possuem.
---
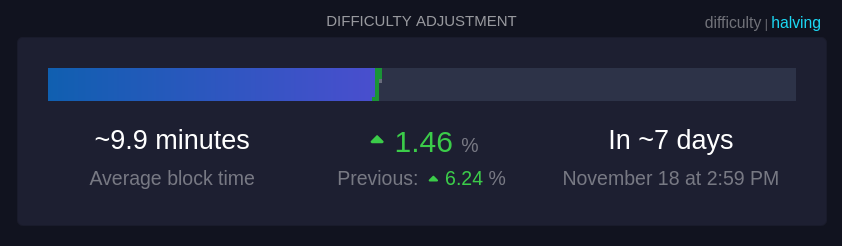
Essa seção mostra informações sobre o ajuste de dificuldade, que ocorre aproximadamente a cada duas semanas.
#### Tempo médio dos blocos (~9,9 minutos):
Este é o tempo médio atual para minerar um bloco na rede. A meta da rede é manter o tempo de bloco em cerca de 10 minutos; um tempo menor indica um aumento na taxa de hash, ou seja, que mais poder computacional foi adicionado à rede.
#### Mudança de dificuldade (+1,46%):
A dificuldade ajusta-se a cada 2016 blocos para manter o tempo médio de bloco próximo de 10 minutos. Um aumento na dificuldade, como +1,46%, indica que a mineração ficou mais difícil devido ao aumento do hashrate, enquanto uma redução na dificuldade indica que o hashrate diminuiu.
#### Tempo até o próximo ajuste:
É o tempo previsto até o próximo ajuste de dificuldade (7 dias, nesse caso), o que é crucial para manter a rede estável e garantir a segurança e a regularidade do processo de mineração.
---
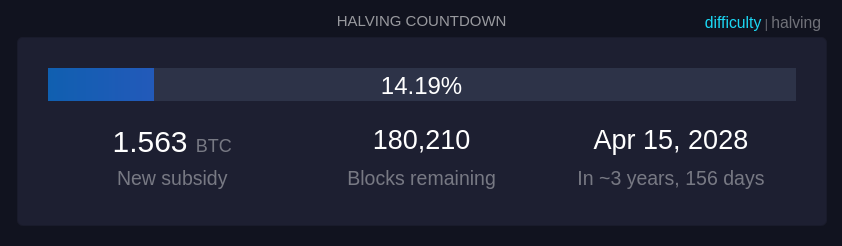
Quanto tempo demora até o próximo halving, um evento no Bitcoin que ocorre aproximadamente a cada 210.000 blocos minerados, ou cerca de quatro anos. Durante o halving, a recompensa que os mineradores recebem por adicionar um novo bloco à blockchain é reduzida pela metade.
---
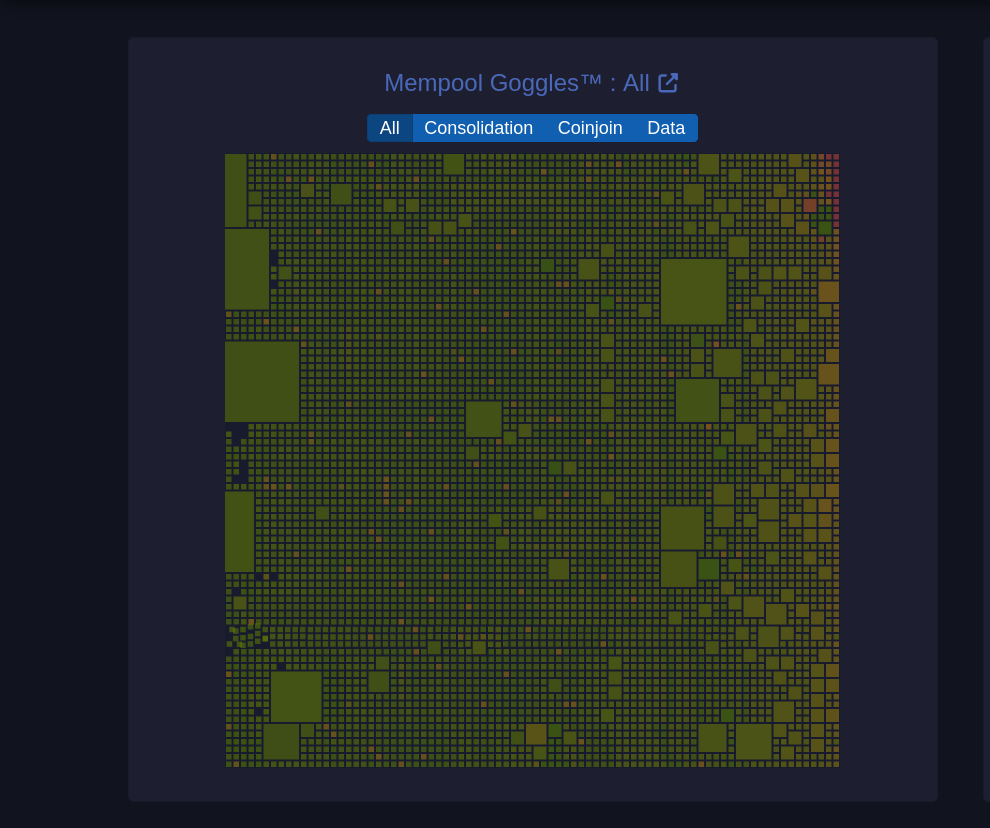
Um diagrama visual da mempool que mostra o estado das transações pendentes na rede.
#### Tamanhos de blocos
O tamanho de cada quadrado representa o tamanho da transação em bytes.
**Filtros (Consolidação, Coinjoin, Dados):** Permite visualizar categorias específicas de transações:
* **Consolidação**: Transações de consolidação agrupam pequenos UTXOs em um único UTXO maior para simplificar e baratear futuras transações. (UTXOs merecem um artigo dedicado)
* **Coinjoin**: Transações CoinJoin são usadas para melhorar a privacidade, misturando transações de vários usuários em uma única transação.
* **Dados**: Mostra transações que contêm dados adicionais, que podem incluir informações não financeiras, como mensagens.
---
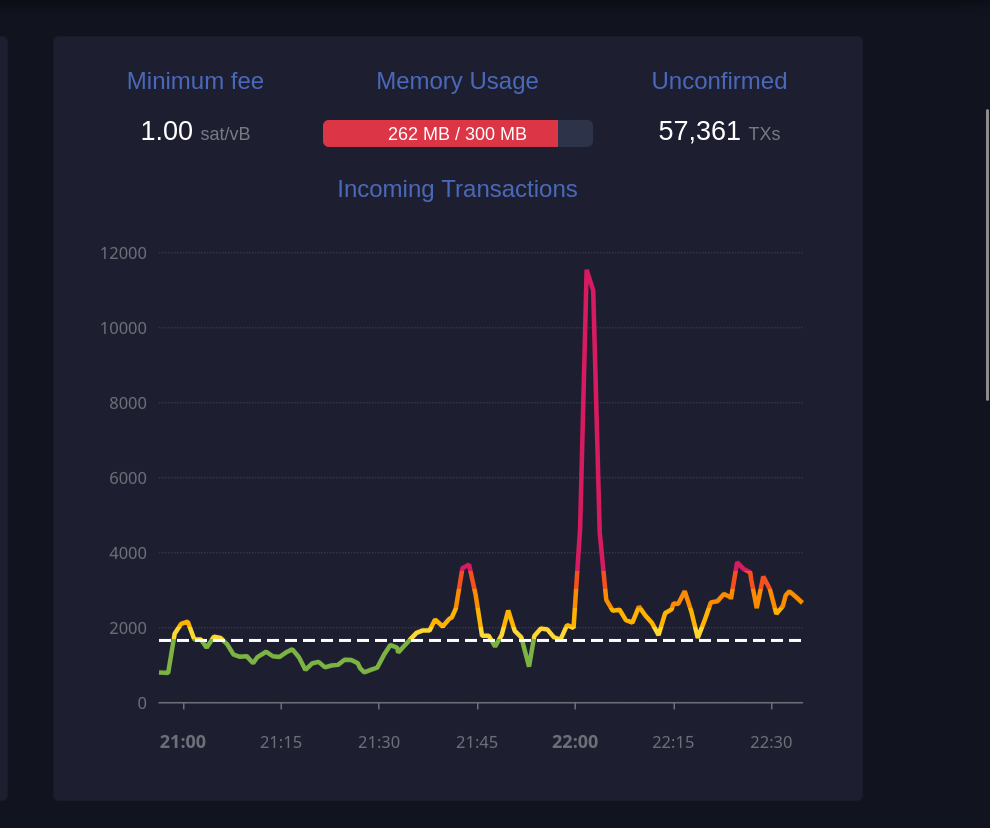
Este gráfico exibe o número de transações recebidas ao longo do tempo.
#### Taxa mínima (1 sat/vB):
Indica a taxa mínima atualmente aceita pela mempool. Se a mempool estiver cheia, transações que paguem menos do que a taxa mínima podem ser excluídas para dar lugar a transações de maior prioridade.
#### Uso de memória (259 MB / 300 MB):
A mempool tem um limite de memória. Quando está cheia, transações de taxa mais baixa podem ser descartadas para abrir espaço para aquelas com taxas mais altas, priorizando-as para inclusão em blocos.
#### Transações não confirmadas (59.361):
Indica o número total de transações pendentes que aguardam confirmação. Quanto maior o número de transações na mempool, maior a probabilidade de que as taxas aumentem para garantir uma confirmação mais rápida.
---

Essa seção mostra transações que foram substituídas utilizando o mecanismo RBF (Replace-By-Fee), que permite substituir uma transação com uma taxa mais alta para acelerar sua confirmação.
#### TXID
Este é o identificador da transação (Transaction ID), exibido parcialmente para abreviar o espaço. Cada transação tem um identificador único na blockchain.
#### Previous fee
Exibe a taxa de transação original paga na primeira tentativa, medida em satoshis por vByte (sat/vB). Esta taxa inicial provavelmente era baixa demais, resultando em uma demora na confirmação.
#### New fee
Mostra a nova taxa de transação, também em satoshis por vByte, definida para substituir a taxa anterior. Uma taxa maior aumenta as chances de inclusão rápida em um bloco.
#### Status (RBF)
RBF indica que a transação foi substituída utilizando o recurso "Replace-By-Fee". Isso significa que a nova transação cancelou e substituiu a original, e o minerador escolherá a transação com a taxa mais alta para incluir no próximo bloco.
---
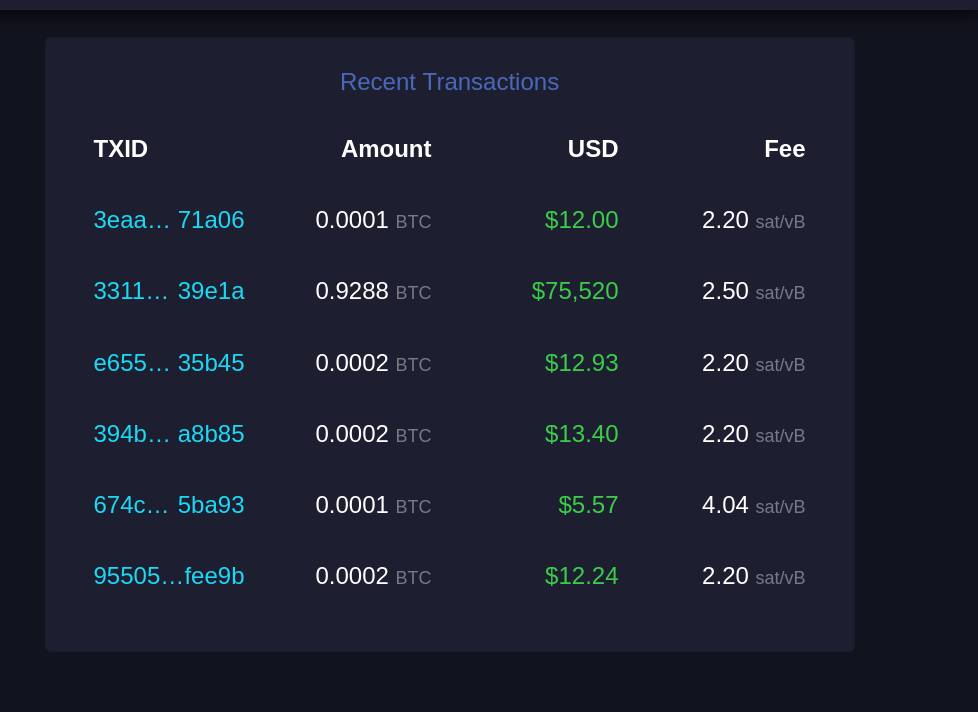
Esta seção lista transações recentes que entraram na mempool e aguardam confirmação.
#### TXID
Similar ao "Recent Replacements", este é o identificador único da transação.
#### Amount
Exibe a quantidade de Bitcoin transferida nessa transação, geralmente em frações de BTC (como 0.0001 BTC). Esta é a quantia enviada pelo remetente ao destinatário.
#### USD
Mostra o valor da transação em dólares americanos (USD), calculado com base na taxa de câmbio atual. Serve para dar uma ideia de quanto a transação representa em moeda fiduciária.
#### Fee
Exibe a taxa de transação paga, em satoshis por vByte (sat/vB). Uma taxa mais alta em relação à média aumenta a probabilidade de confirmação mais rápida, pois as transações com taxas mais elevadas são priorizadas pelos mineradores.
---
E acabou. Espero que isso tenha sido útil para você e tenha agregado mais entendimento sobre esse complexo e maravilhoso mundo do Bitcoin. Se foi, considere compartilhar com alguém que precise. E se tem sugestões de melhoria, por favor, não deixe de comentar, o conhecimento está dispero na sociedade.
Por fim, stay humble and stack sats!
-

@ ec09d831:42c80ce4
2024-11-11 22:18:22
-*Doğru diye bir şey yoktur.*
-**Peki bu doğru mu?**
-*Gerçek bilinemez.*
-**Nereden biliyorsun?**
-*Kesinlik yoktur.*
-**Kesinlikle mi?**
-*Sadece beş duyunuz gerçek bilgiyi sağlar.*
-**Beş duyudan hangisi bu kanıya vardı?**
-*Mantıksal argümanlar KANIT değildir.*
-**Bunun için kanıtınız nedir?**
-*Sadece fiziksel âlem gerçektir.*
-**Bu savın kendisi bile fiziksel âlemde geliştirilmiş değildir, dolayısıyla kendi kendini çürütür.**
-

@ f462d21e:1390b6b1
2024-11-10 11:44:59
eyJfaWQiOiIxMGRmODZiMS02NTdjLTQwNjUtYjVjOC1kNmY2YmJlNjRhN2IiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwidXNlcm5hbWUiOiJqb2UiLCJhZFR5cGUiOiJPTkxJTkVfU0VMTCIsImNvdW50cnkiOiJVbml0ZWQgS2luZ2RvbSIsImNvdW50cnlDb2RlIjoiR0IiLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6IlZFTk1PIiwicHJpY2VJbnB1dFR5cGUiOiJNQVJLRVQiLCJtYXJnaW4iOjMsImZpeGVkUHJpY2UiOjAsIm1pbkFtb3VudCI6MCwibWF4QW1vdW50IjowLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCByYXRlcyByZWFsbHkiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDFUMDc6MTk6MjEuMDk5WiIsIm1hcmtldFByaWNlIjoxNjUuMzF9
-

@ a10260a2:caa23e3e
2024-11-10 04:35:34
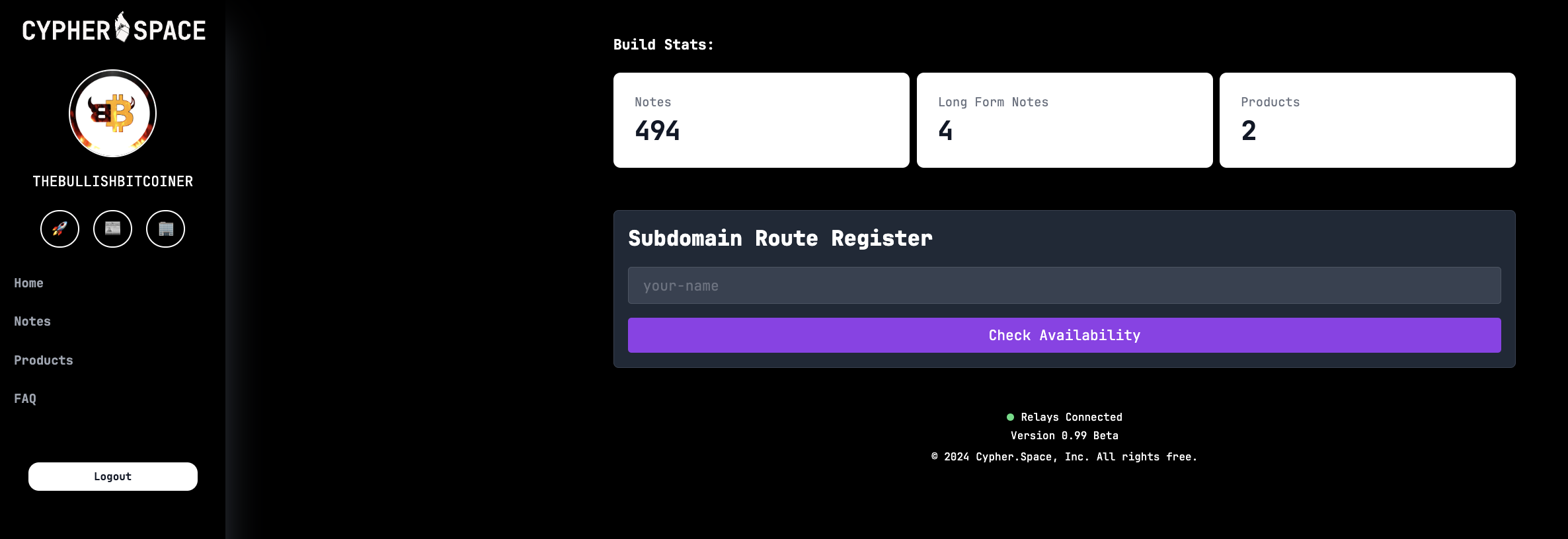
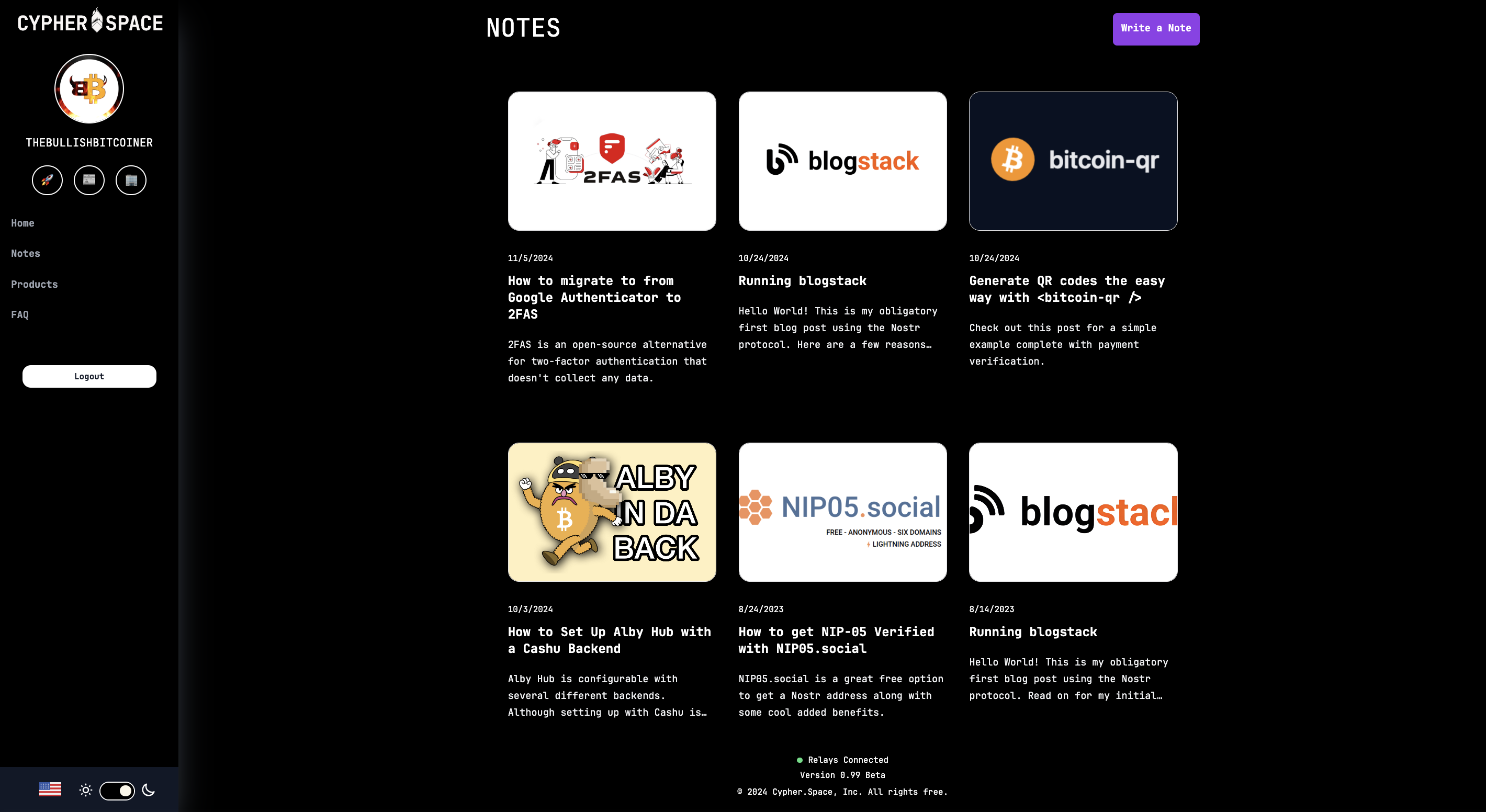
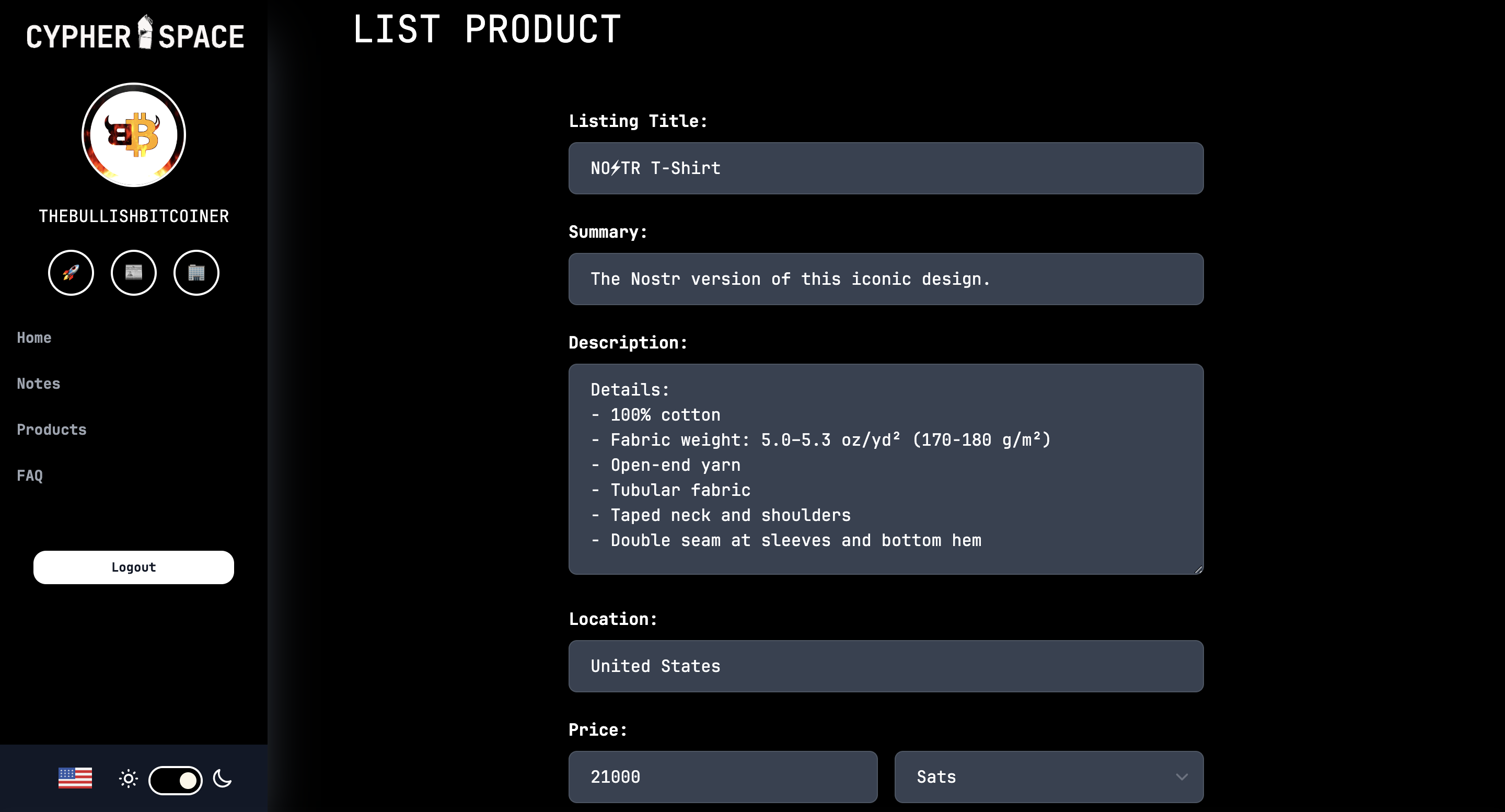
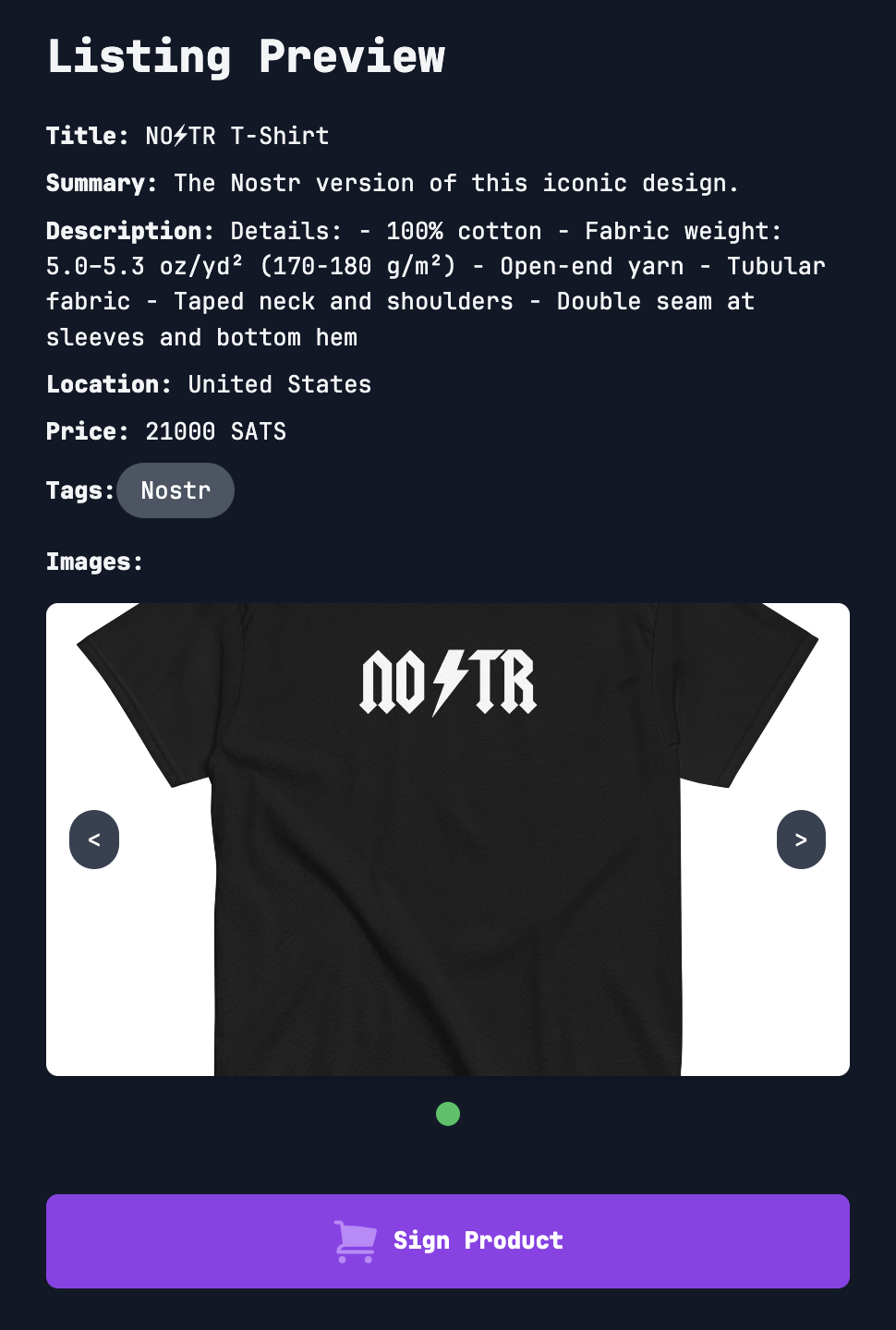
nostr:npub1nkmta4dmsa7pj25762qxa6yqxvrhzn7ug0gz5frp9g7p3jdscnhsu049fn added support for [classified listings (NIP-99)](https://github.com/sovbiz/Cypher-Nostr-Edition/commit/cd3bf585c77a85421de031db1d8ebd3911ba670d) about a month ago and recently announced this update that allows for creating/editing listings and blog posts via the dashboard.
In other words, listings created on the website are also able to be viewed and edited on other Nostr apps like Amethyst and Shopstr. Interoperability FTW.
I took some screenshots to give you an idea of how things work.
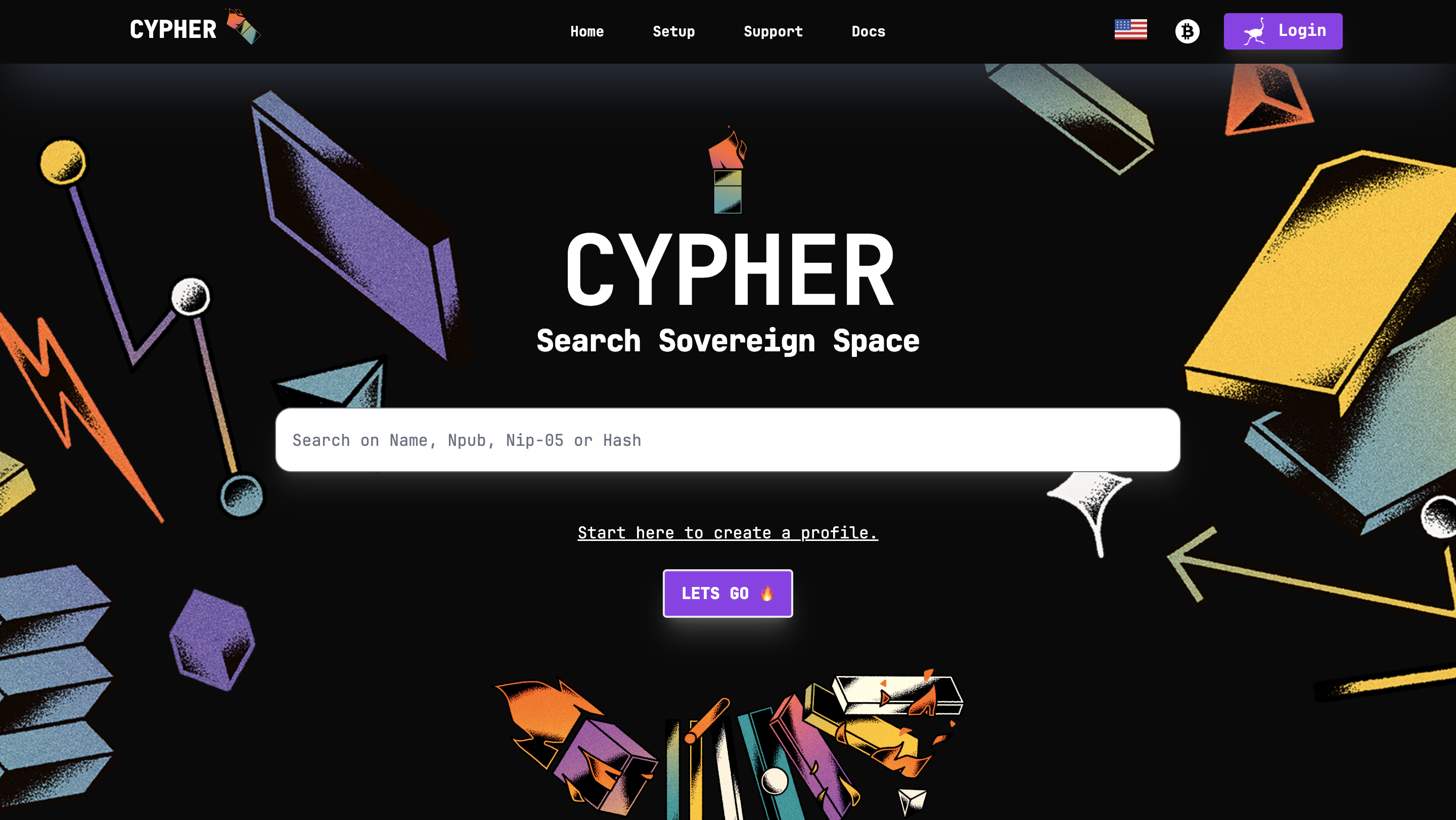
The [home page](https://cypher.space/) is clean with the ability to search for profiles by name, npub, or Nostr address (NIP-05).
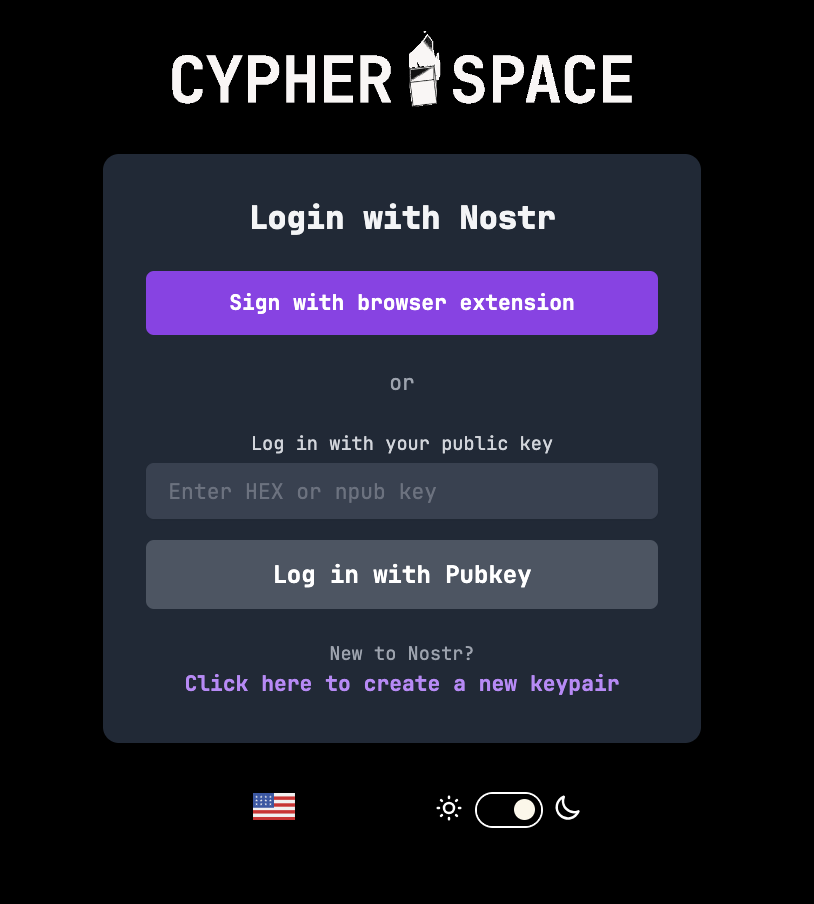
Clicking login allows signing in with a browser extension.
The dashboard gives an overview of the amount of notes posted (both short and long form) and products listed.
Existing blog posts (i.e. long form notes) are synced.
Same for product listings. There’s a nice interface to create new ones and preview them before publishing.
That’s all for now. As you can see, super slick stuff!
Bullish on Cypher.
So much so I had to support the project and buy a subdomain. 😎
https://bullish.cypher.space
originally posted at https://stacker.news/items/760592
-

@ b34f99f1:006b0fcc
2024-11-09 17:03:35
eyJfaWQiOiI5NDEyN2JmZi00ZDhlLTRmODUtOThiMy1kNGRhNDNhMTgxODQiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiTkFUSU9OQUxfQkFOSyIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjozLCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjEwMCwibWF4QW1vdW50IjowLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCByYXRlcyBqdXN0IGZvciB5b3UiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMTQ6Mzk6MjMuNzU5WiIsIm1hcmtldFByaWNlIjoxNjMuOX0=
-

@ b34f99f1:006b0fcc
2024-11-09 17:03:02
deleted
-

@ b34f99f1:006b0fcc
2024-11-09 17:02:11
eyJfaWQiOiI0NTljZTMxMC1mNDlkLTQ2NDAtYTNmZi0xODVjYTZiOGU3MDMiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiTE9DQUxfQlVZIiwiY291bnRyeSI6IlVuaXRlZCBTdGF0ZXMgb2YgQW1lcmljYSIsImNvdW50cnlDb2RlIjoiVVMiLCJsYXQiOjI3Ljk0Nzc2LCJsb24iOi04Mi40NTg0NDQsImdlY29kZSI6eyJwbGFjZV9pZCI6MjcwMDI2NzQ0LCJsaWNlbmNlIjoiRGF0YSDCqSBPcGVuU3RyZWV0TWFwIGNvbnRyaWJ1dG9ycywgT0RiTCAxLjAuIGh0dHBzOi8vb3NtLm9yZy9jb3B5cmlnaHQiLCJvc21fdHlwZSI6InJlbGF0aW9uIiwib3NtX2lkIjoxMjMyMTE1NiwibGF0IjoiMjcuOTQ3OTIiLCJsb24iOiItODIuNDU4MTIxMDYzNjExOTciLCJkaXNwbGF5X25hbWUiOiJSaXZlcnNpZGUsIFRhbXBhLCBIaWxsc2Jvcm91Z2ggQ291bnR5LCBGbG9yaWRhLCBVbml0ZWQgU3RhdGVzIiwiYWRkcmVzcyI6eyJoYW1sZXQiOiJSaXZlcnNpZGUiLCJjaXR5IjoiVGFtcGEiLCJjb3VudHkiOiJIaWxsc2Jvcm91Z2ggQ291bnR5Iiwic3RhdGUiOiJGbG9yaWRhIiwiSVNPMzE2Ni0yLWx2bDQiOiJVUy1GTCIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIiwiY291bnRyeV9jb2RlIjoidXMifSwiYm91bmRpbmdib3giOlsiMjcuOTQ3NDg2MiIsIjI3Ljk0ODM2NDEiLCItODIuNDU4OTg5MSIsIi04Mi40NTgwMDUzIl19LCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MTAsImZpeGVkUHJpY2UiOjAsImJ1eWVyU2V0dGxlbWVudEFkZHJlc3MiOiIiLCJtaW5BbW91bnQiOjUwMDAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwibXNnIjoid2FpdCBmb3IgbWUgYXQgYnVzIHN0YXRpb24iLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMjA6NDU6MTYuNjgxWiIsIm1hcmtldFByaWNlIjoxNjUuNH0=
-

@ bcea2b98:7ccef3c9
2024-11-09 17:01:32
Weekends are the perfect time to unwind, explore, or spend time doing what we love. How would you spend your ideal weekend? Would it be all about relaxation, or would you be out and about?
For me, an ideal weekend would start with a slow Saturday morning, a good book and coffee. Then I would spend the afternoon exploring local trails and looking for snacks. Then always a slow Sunday night hopefully.
originally posted at https://stacker.news/items/760492
-

@ b34f99f1:006b0fcc
2024-11-09 16:35:11
eyJfaWQiOiI0NzgyYTkzNC02ZTUzLTRlYTctOWUwOC04YTAwZjJmNGQ4NTAiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiQ1JZUFRPQ1VSUkVOQ1kiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJmaXhlZFByaWNlIjoxOTAsIm1pbkFtb3VudCI6MjAwLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiJsdGMgfCBidGMiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMTQ6NDA6MjYuODk0WiJ9
-

@ 1eb966a6:e3eddf94
2024-11-09 13:19:43
eyJfaWQiOiJhNThkNzNlMi05NzAwLTQ3ZmUtODZiMy0xZGU0NWQwZGRhZDIiLCJwdWJsaWNLZXkiOiIxZWI5NjZhNmEwMjE4YWJhNTIwYWFhYzkzYmU3ZGQ4YmYzODMwZmM3NzEwYmM4MGNhZWEzYTZhNWUzZWRkZjk0IiwidXNlcm5hbWUiOiJoYW5rIiwiYWRUeXBlIjoiTE9DQUxfU0VMTCIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIG9mIEFtZXJpY2EiLCJjb3VudHJ5Q29kZSI6IlVTIiwibGF0IjozNC4wNTM2OTEsImxvbiI6LTExOC4yNDI3NjYsImdlY29kZSI6eyJwbGFjZV9pZCI6Mjg0ODczMDQ4LCJsaWNlbmNlIjoiRGF0YSDCqSBPcGVuU3RyZWV0TWFwIGNvbnRyaWJ1dG9ycywgT0RiTCAxLjAuIGh0dHBzOi8vb3NtLm9yZy9jb3B5cmlnaHQiLCJvc21fdHlwZSI6InJlbGF0aW9uIiwib3NtX2lkIjo2MzMzMTQ1LCJsYXQiOiIzNC4wNTM2OTYwNSIsImxvbiI6Ii0xMTguMjQyOTIxMjE4MzMzOTUiLCJkaXNwbGF5X25hbWUiOiJMb3MgQW5nZWxlcyBDaXR5IEhhbGwsIDIwMCwgTm9ydGggU3ByaW5nIFN0cmVldCwgQ2l2aWMgQ2VudGVyLCBEb3dudG93biwgTG9zIEFuZ2VsZXMsIExvcyBBbmdlbGVzIENvdW50eSwgQ2FsaWZvcm5pYSwgOTAwMTIsIFVuaXRlZCBTdGF0ZXMiLCJhZGRyZXNzIjp7ImJ1aWxkaW5nIjoiTG9zIEFuZ2VsZXMgQ2l0eSBIYWxsIiwiaG91c2VfbnVtYmVyIjoiMjAwIiwicm9hZCI6Ik5vcnRoIFNwcmluZyBTdHJlZXQiLCJxdWFydGVyIjoiQ2l2aWMgQ2VudGVyIiwic3VidXJiIjoiRG93bnRvd24iLCJjaXR5IjoiTG9zIEFuZ2VsZXMiLCJjb3VudHkiOiJMb3MgQW5nZWxlcyBDb3VudHkiLCJzdGF0ZSI6IkNhbGlmb3JuaWEiLCJJU08zMTY2LTItbHZsNCI6IlVTLUNBIiwicG9zdGNvZGUiOiI5MDAxMiIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIiwiY291bnRyeV9jb2RlIjoidXMifSwiYm91bmRpbmdib3giOlsiMzQuMDUzMDE0MSIsIjM0LjA1NDM3MTMiLCItMTE4LjI0MzUzIiwiLTExOC4yNDIwMDUyIl19LCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjowLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsIm1zZyI6Im1lZXQgbWUgb25seSBpbiBwdWJsaWMiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMDg6NTI6MjYuNzkzWiIsIm1hcmtldFByaWNlIjoxNjIuMTd9
-

@ 1eb966a6:e3eddf94
2024-11-09 13:18:54
deleted
-

@ 1eb966a6:e3eddf94
2024-11-09 13:18:25
deleted
-

@ b34f99f1:006b0fcc
2024-11-09 11:47:09
deleted
-

@ b34f99f1:006b0fcc
2024-11-09 11:43:11
deleted
-

@ b34f99f1:006b0fcc
2024-11-09 11:29:46
deleted
-

@ b34f99f1:006b0fcc
2024-11-09 11:25:16
deleted
-

@ fd208ee8:0fd927c1
2024-11-09 09:21:19
## Drumroll, please....
In a previous article, I introduced the concept of [relay communities](nostr:naddr1qvzqqqr4gupzplfq3m5v3u5r0q9f255fdeyz8nyac6lagssx8zy4wugxjs8ajf7pqydhwumn8ghj7argv4nx7un9wd6zumn0wd68yvfwvdhk6tcpr3mhxue69uhhg6r9vd5hgctyv4kzumn0wd68yvfwvdhk6tcqp5cnwvesxcunjwpcxymrsvgwmj66e).
The ink had barely dried, on that set of instructions, before one of my favorite Nostr devs, [ثعبان](nostr:nprofile1qythwumn8ghj7enjv4h8xtnwdaehgu339e3k7mf0qy88wumn8ghj7mn0wvhxcmmv9uqzqla9dawkjc4trc7dgf88trpsq2uxvhmmpkxua607nc5g6a634sv598gk68), rolled out the alpha version of a relay-community client.
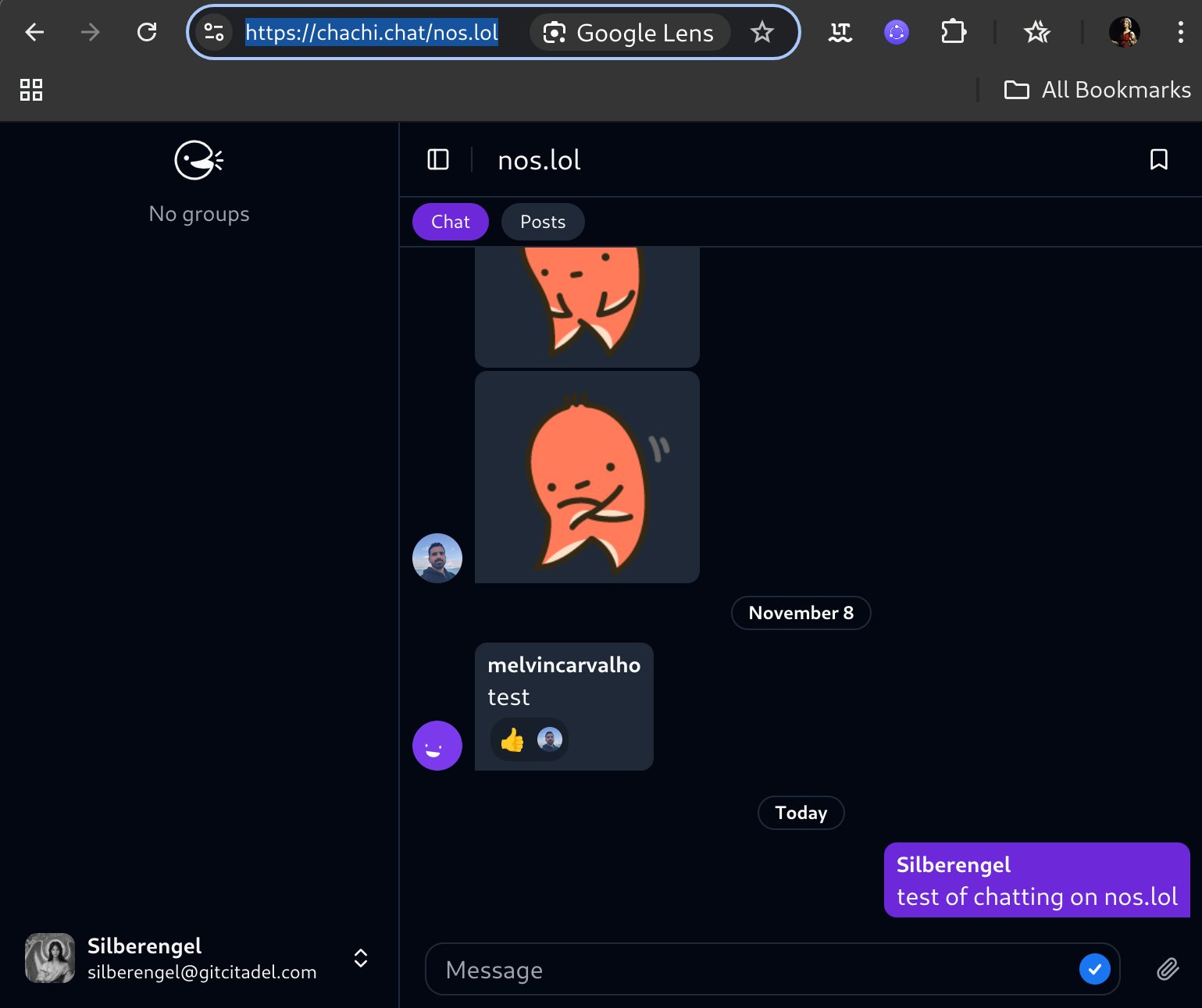
Obviously, it's still a bit of a construction site, but you can check out how it'd work, for your community, by test-driving the functionality on your own relay. Simply type _https://chachi.chat/_ followed by the name of your relay. For instance, one gigantic relay community, where nearly everyone can try out the functionality, is [nos.lol](https://chachi.chat/nos.lol).
If your relay community does not require AUTH to read, anyone can pull your chatter into their own relay and respond to it there. That is because every chat entry is simply a kind 09 event, and unprotected events are not private data.
For instance, I moderate one community [theforest.nostr1.com](https://chachi.chat/theforest.nostr1.com), that is openly readable, and that's probably where most of the chatter on [nostr.band](https://chachi.chat/relay.nostr.band) is coming from, as that relay is an aggregator of the content of many other relays. However, I have another community, [gitcitadel.nostr1.com](https://chachi.chat/gitcitadel.nostr1.com) that is AUTH-protected, whose content stays private to those allowed on that relay. Communities are where write-protected and AUTH relays are going to really shine, as they create an environment similar to Telegram, but where you control the dataset, you decide which types of events to support, and you design the client, the algos, the moderation, the visibility, etc.
With communities, **the onboarding experience is seamless**: just get a browser extension and a nsec, login, start writing and posting, and _start receiving responses_. Active, chatty, well-moderated communities will be more attractive to onboard to, than chaotic, spammy, or empty communities. This means that you don't have to have the killer entry under "Posts" (where kind 11 and eventually kind 01 posts appear), just to get some interaction. Chat is the Great Equalizer.
So, we're testing both setups, with [cloudfodder](nostr:nprofile1qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3eryvfwvdhk6tcqyp7vx29q3hdj4l0elxl800hlfjp538le09epsf7k9zj59ue2y37qu84upun) adjusting the relay faucet code and ثعبان is fiddling with the community client settings, to make the most-comfortable situation for both kinds.
## This is the signal
This #Chachi client, of course, is merely the first horse out of the gate. There are already other devs hacking away at variants of the same concept, such as [#Flotilla](https://flotilla.coracle.social/), I'm sure CloudFodder is also cooking, later versions of #Alexandria will integrate theforest community, and etc. etc. etc.
It remains to be seen, how many new use cases can be dreamt up, with this new architecture, but I am quite certain, that this is the beginning of the end of Nostr 1.0. We are moving up and out, and away from the stultifying and limiting concept of Twitter 2.0, toward

Soon, we will enter Nostr 2.0. See you on the other side.
-

@ a39d19ec:3d88f61e
2024-11-09 09:17:35
##### What do you even print with it besides decorative objects?
This kind of question still is a common one when talking about 3d printing.
With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot.
The second thing I show you is a "Swiss Keyholder"
## Swiss Keyholder
There are many designs of such a Keyholder to download and print. As this is one of the first prints I have done in ABS back in 2014 on a "Up!Mini" 3d printer I can't find where I downloaded it.
I like the slim design and that I don't have any "loose" keys in my pocket. It is just tidy in my pocket. This is probably the most used print of mine.
Edit:
You can download the file here:
[Thingiverse](https://www.thingiverse.com/thing:98427)

-

@ a95c6243:d345522c
2024-11-08 20:02:32
*Und plötzlich weißt du:
Es ist Zeit, etwas Neues zu beginnen
und dem Zauber des Anfangs zu vertrauen.
Meister Eckhart*
**Schwarz, rot, gold leuchtet es im Kopf des Newsletters der deutschen Bundesregierung,** der mir freitags ins Postfach flattert. Rot, gelb und grün werden daneben sicher noch lange vielzitierte Farben sein, auch wenn diese nie geleuchtet haben. Die Ampel hat sich gerade selber den Stecker gezogen – und hinterlässt einen wirtschaftlichen und gesellschaftlichen Trümmerhaufen.
**Mit einem bemerkenswerten [Timing](https://transition-news.org/donald-trump-grossmaul-oder-hoffnungstrager) hat die deutsche Regierungskoalition** am Tag des «Comebacks» von Donald Trump in den USA endlich ihr Scheitern besiegelt. Während der eine seinen Sieg bei den Präsidentschaftswahlen feierte, erwachten die anderen jäh aus ihrer [Selbsthypnose](https://ansage.org/schwer-traumatisiert-nach-trumps-sieg-dreht-die-politmediale-linksgruene-sekte-durch/) rund um Harris-Hype und Trump-Panik – mit teils erschreckenden [Auswüchsen](https://archive.is/7tDhY). Seit Mittwoch werden die Geschicke Deutschlands nun von einer rot-grünen Minderheitsregierung «geleitet» und man steuert auf Neuwahlen zu.
**Das [Kindergarten](https://www.spiegel.de/politik/deutschland/christian-lindner-auch-die-fdp-will-wieder-einen-eigenen-wirtschaftsgipfel-abhalten-a-a8a4e868-10b1-426e-adb0-e5a6d42f7c46)-Gehabe um zwei konkurrierende Wirtschaftsgipfel letzte Woche** war bereits bezeichnend. In einem Strategiepapier gestand Finanzminister Lindner außerdem den «Absturz Deutschlands» ein und offenbarte, dass die wirtschaftlichen Probleme teilweise von der Ampel-Politik [«vorsätzlich herbeigeführt»](https://www.t-online.de/nachrichten/deutschland/innenpolitik/id_100522112/fdp-chef-lindner-und-sein-grundsatzpapier-die-scheidung-von-der-ampel-.html) worden seien.
**Lindner und weitere FDP-Minister wurden also vom Bundeskanzler entlassen.** Verkehrs- und [Digitalminister Wissing](https://transition-news.org/raus-aus-der-komfortzone-es-lohnt-sich) trat flugs aus der FDP aus; deshalb darf er nicht nur im Amt bleiben, sondern hat zusätzlich noch das Justizministerium übernommen. Und mit [Jörg Kukies](https://norberthaering.de/news/joerg-kukies/) habe Scholz «seinen Lieblingsbock zum Obergärtner», sprich: Finanzminister befördert, meint Norbert Häring.
**Es gebe keine Vertrauensbasis für die weitere Zusammenarbeit mit der FDP,** hatte der Kanzler erklärt, Lindner habe zu oft sein Vertrauen gebrochen. Am 15. Januar 2025 werde er daher im Bundestag die Vertrauensfrage stellen, was ggf. den Weg für vorgezogene Neuwahlen freimachen würde.
**Apropos Vertrauen: Über die Hälfte der Bundesbürger glauben, dass sie ihre Meinung nicht frei sagen können.** Das ging erst kürzlich aus dem diesjährigen [«Freiheitsindex»](https://www.schwaebische.de/politik/forscher-beim-vertrauen-in-staat-und-medien-zerreisst-es-uns-gerade-3034357) hervor, einer Studie, die die Wechselwirkung zwischen Berichterstattung der Medien und subjektivem Freiheitsempfinden der Bürger misst. «Beim Vertrauen in Staat und Medien zerreißt es uns gerade», kommentierte dies der Leiter des Schweizer Unternehmens Media Tenor, das die Untersuchung zusammen mit dem Institut für Demoskopie Allensbach durchführt.
**«Die absolute Mehrheit hat [absolut die Nase voll](https://archive.is/yRxwR)»,** titelte die *Bild* angesichts des «Ampel-Showdowns». Die Mehrheit wolle Neuwahlen und die Grünen sollten zuerst gehen, lasen wir dort.
**Dass «Insolvenzminister» Robert Habeck heute seine Kandidatur für das Kanzleramt verkündet hat,** kann nur als Teil der politmedialen Realitätsverweigerung verstanden werden. Wer allerdings denke, schlimmer als in Zeiten der Ampel könne es nicht mehr werden, sei reichlich optimistisch, schrieb Uwe Froschauer bei *Manova*. Und er kenne [Friedrich Merz](https://www.manova.news/artikel/der-kriegsgeile-blackrocker) schlecht, der sich schon jetzt rhetorisch auf seine Rolle als oberster Feldherr Deutschlands vorbereite.
**Was also tun? Der Schweizer Verein [«Losdemokratie»](https://zeitpunkt.ch/node/40968) will eine Volksinitiative lancieren,** um die Bestimmung von Parlamentsmitgliedern per Los einzuführen. Das Losverfahren sorge für mehr Demokratie, denn als Alternative zum Wahlverfahren garantiere es eine breitere Beteiligung und repräsentativere Parlamente. Ob das ein Weg ist, sei dahingestellt.
**In jedem Fall wird es notwendig sein, unsere Bemühungen um [Freiheit und Selbstbestimmung](https://transition-news.org/alternative-medien-in-der-krise-zensur-kontrollverlust-und-die-suche-nach)** zu verstärken. Mehr Unabhängigkeit von staatlichen und zentralen Institutionen – also die Suche nach dezentralen Lösungsansätzen – gehört dabei sicher zu den Möglichkeiten. Das gilt sowohl für jede/n Einzelne/n als auch für Entitäten wie die alternativen Medien.
---
Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/es-kann-nur-besser-werden-aber-wie)* erschienen.
-

@ fd208ee8:0fd927c1
2024-11-08 10:27:40
## You have no idea
I regularly read comments from people, on here, wondering how it's possible to marry -- or even simply be friends! -- with someone who doesn't agree with you on politics. I see this sentiment expressed quite often, usually in the context of Bitcoin, or whatever _pig is currently being chased through the village_, as they say around here.

It seems rather sensible, but I don't think it's as hard, as people make it out to be. Further, I think it's a dangerous precondition to set, for your interpersonal relationships, because the political field is constantly in flux. If you determine who you will love, by their opinions, do you stop loving them if their opinions change, or if the opinions they have become irrelevant and a new set of opinions are needed -- and their new ones don't match your new ones? We could see this happen to relationships en masse, during the Covid Era, and I think it happens every day, in a slow grind toward the disintegration of interpersonal discourse.
I suspect many people do stop loving, at that point, as they never really loved the other person for their own sake, they loved the other person because they thought the other person was exactly like they are. But no two people are alike, and the longer you are in a relationship with someone else, the more the initial giddiness wears off and the trials and tribulations add up, the more you notice how very different you actually are. This is the point, where best friends and romantic couples say, _We just grew apart._
But you were always apart. You were always two different people. You just didn't notice, until now.

I've also always been surprised at how many same-party relationships disintegrate because of some disagreement over some particular detail of some particular topic, that they generally agree on. To me, it seems like an irrelevant side-topic, but _they can't stand to be with this person_... and they stomp off. So, I tend to think that it's less that opinions need to align to each other, but rather that opinions need to align in accordance with the level of interpersonal tolerance they can bring into the relationship.
## I was raised by relaxed revolutionaries
Maybe I see things this way because my parents come from two diverging political, cultural, national, and ethnic backgrounds, and are prone to disagreeing about a lot of "important" (to people outside their marriage) things, but still have one of the healthiest, most-fruitful, and most long-running marriages of anyone I know, from that generation. My parents, you see, aren't united by their opinions. They're united by their relationship, which is something _outside_ of opinions. Beyond opinions. Relationships are what turn two different people into one, cohesive unit, so that they slowly grow together. Eventually, even their faces merge, and their biological clocks tick to the same rhythm. They eventually become one entity that contains differing opinions about the same topics.
It's like magic, but it's the result of a mindset, not a worldview.
Or, as I like to quip:
> The best way to stay married, is to not get divorced.

My parents simply determined early on, that they would stay together, and whenever they would find that they disagreed on something that _didn't directly pertain to their day-to-day existence with each other_ they would just agree-to-disagree about that, or roll their eyes, and move on. You do you. Live and let live.
My parents have some of the most strongly held personal opinions of any people I've ever met, but they're also incredibly tolerant and can get along with nearly anyone, so their friends are a confusing hodgepodge of _people we liked and found interesting enough to keep around_. Which makes their house parties really fun, and highly unusual, in this day and age of mutual-damnation across the aisle.

The things that did affect them, directly, like which school the children should attend or which country they should live in, etc. were things they'd sit down and discuss, and somehow one opinion would emerge, and they'd again... move on.
And that's how my husband and I also live our lives, and it's been working surprisingly well. No topics are off-limits to discussion (so long as you don't drone on for too long), nobody has to give up deeply held beliefs, or stop agitating for the political decisions they prefer.
You see, we didn't like that the other always had the same opinion. We liked that the other always held their opinions strongly. That they were passionate about their opinions. That they were willing to voice their opinions; sacrifice to promote their opinions. And that they didn't let anyone browbeat or cow them, for their opinions, not even their best friends or their spouse. But that they were open to listening to the other side, and trying to wrap their mind around the possibility that they _might just be wrong about something_.

We married each other because we knew: this person really cares, this person has thought this through, and they're in it, to win it. What "it" is, is mostly irrelevant, so long as it doesn't entail torturing small animals in the basement, or raising the children on a diet of Mountain Dew and porn, or something.
Live and let live. At least, it's never boring. At least, there's always something to ~~argue~~ talk about. At least, we never think... we've just grown apart.
-

@ 13351007:eccd002a
2024-11-08 05:32:41
eyJfaWQiOiI0OTNkNDQyNS01YTRiLTQ2YjYtYjFhNC0yZTEyNjZlYTEyNDYiLCJwdWJsaWNLZXkiOiIxZWI5NjZhNmEwMjE4YWJhNTIwYWFhYzkzYmU3ZGQ4YmYzODMwZmM3NzEwYmM4MGNhZWEzYTZhNWUzZWRkZjk0IiwidXNlcm5hbWUiOiJoYW5rIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiTkFUSU9OQUxfQkFOSyIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjoiMyIsImZpeGVkUHJpY2UiOiIiLCJtaW5BbW91bnQiOiIxMDAiLCJtYXhBbW91bnQiOiIiLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiZmFzdCBhbmQgYmVzdCB0cmFkZXIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOiIiLCJmaXJzdFRpbWVMaW1pdEFzc2V0IjoiIiwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMS0wOFQwNTozMjo0MS44MzZaIiwibWFya2V0UHJpY2UiOjE2NC4xM30=
-

@ 4ba8e86d:89d32de4
2024-11-07 13:56:21
Tutorial feito por Grom mestre⚡poste original abaixo:
http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/240277/tutorial-criando-e-acessando-sua-conta-de-email-pela-i2p?show=240277#q240277
Bom dia/tarde/noite a todos os camaradas.
Seguindo a nossa série de tutoriais referentes a tecnologias essenciais para a segurança e o anonimato dos usuários, sendo as primeiras a openPGP e a I2P, lhes apresento mais uma opção para expandir os seus conhecimentos da DW.
Muitos devem conhecer os serviços de mail na onion como DNMX e mail2tor, mas e que tal um serviço de email pela I2P. Nesse tutorial eu vou mostrar a vocês como criar a sua primeira conta no hq.postman.i2p e a acessar essa conta.
É importante que vocês tenham lido a minha primeira série de tutoriais a respeito de como instalar, configurar e navegar pela I2P nostr:nevent1qqsyjcz2w0e6d6dcdeprhuuarw4aqkw730y542dzlwxwssneq3mwpaspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsyp5vcq Esse tutorial é um pré-requisito para o seguinte e portanto recomendo que leia-os antes de prosseguir com o seguinte tutorial. O tutorial de Kleopatra nostr:nevent1qqs8h7vsn5j6qh35949sa60dms4fneussmv9jd76n24lsmtz24k0xlqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgecq8f7 é complementar dado que é extremamente recomendado assinar e criptografar as mensagens que seguem por emails pela DW.
Sem mais delongas, vamos ao tutorial de fato.
## 1. Criando uma conta de email no hq.postman
Relembrando: Esse tutorial considera que você já tenha acesso à I2P.
Entre no seu navegador e acesse o endereço hq.postman.i2p. O roteador provavelmente já contém esse endereço no seu addressbook e não haverá a necessidade de inserir o endereço b32 completo.
Após entrar no site vá para a página '1 - Creating a mailbox'
https://image.nostr.build/d850379fe315d2abab71430949b06d3fa49366d91df4c9b00a4a8367d53fcca3.jpg
Nessa página, insira as credenciais de sua preferências nos campos do formulário abaixo. Lembre-se que o seu endereço de email aceita apenas letras e números. Clique em 'Proceed' depois que preencher todos os campos.
https://image.nostr.build/670dfda7264db393e48391f217e60a2eb87d85c2729360c8ef6fe0cf52508ab4.jpg
Uma página vai aparecer pedindo para confirmar as credenciais da sua nova conta. Se tudo estiver certo apenas clique em 'Confirm and Create Mailbox'. Se tudo ocorrer como conforme haverá uma confirmação de que a sua nova conta foi criada com sucesso. Após isso aguarde por volta de 5 minutos antes de tentar acessá-la, para que haja tempo suficiente para o servidor atualizar o banco de dados.
https://image.nostr.build/ec58fb826bffa60791fedfd9c89a25d592ac3d11645b270c936c60a7c59c067f.jpg
https://image.nostr.build/a2b7710d1e3cbb36431acb9055fd62937986b4da4b1a1bbb06d3f3cb1f544fd3.jpg
Pronto! Sua nova conta de email na I2P foi criada. Agora vamos para a próxima etapa: como acessar a sua conta via um cliente de email.
## 2. Configurando os túneis cliente de SMTP e POP3
O hq.postman não possui um cliente web que nos permite acessar a nossa conta pelo navegador. Para isso precisamos usar um cliente como Thunderbird e configurar os túneis cliente no I2Pd que serão necessários para o Thunderbird se comunicar com o servidor pela I2P.
Caso não tenha instalado o Thunderbird ainda, faça-o agora antes de prosseguir.
Vamos configurar os túneis cliente do servidor de email no nosso roteador. Para isso abra um terminal ou o seu gestor de arquivos e vá para a pasta de configuração de túneis do I2P. Em Linux esse diretório se localiza em /etc/i2pd/tunnels.d. Em Windows, essa pasta se localiza em C:\users\user\APPDATA\i2pd.
Na pasta tunnels.d crie dois arquivos: smtp.postman.conf e pop-postman.conf. Lembre-se que em Linux você precisa de permissões de root para escrever na pasta de configuração. Use o comando sudoedit <nome_do_arquivo> para isso.
Edite-os conforme as imagens a seguir:
Arquivo pop-postman.conf
https://image.nostr.build/7e03505c8bc3b632ca5db1f8eaefc6cecb4743cd2096d211dd90bbdc16fe2593.jpg
Arquivo smtp-postman.conf
https://image.nostr.build/2d06c021841dedd6000c9fc2a641ed519b3be3c6125000b188842cd0a5af3d16.jpg
Salve os arquivos e reinicie o serviço do I2Pd. Em Linux isso é feito pelo comando:
```
sudo systemctl restart i2pd
```
Entre no Webconsole do I2Pd pelo navegador (localhost:7070) e na seção I2P Tunnels, verifique se os túneis pop-postman e smtp-postman foram criados, caso contrário verifique se há algum erro nos arquivos e reinicie o serviço.
Com os túneis cliente criados, vamos agora configurar o Thunderbird
## 3. Configurando o Thunderbird para acessar a nossa conta
Abra o Thunderbird e clique em criar uma nova conta de email. Se você não tiver nenhum conta previamente presente nele você vai ser diretamente recebido pela janela de criação de conta a seguir.
https://image.nostr.build/e9509d7bd30623716ef9adcad76c1d465f5bc3d5840e0c35fe4faa85740f41b4.jpg
https://image.nostr.build/688b59b8352a17389902ec1e99d7484e310d7d287491b34f562b8cdd9dbe8a99.jpg
Coloque as suas credenciais, mas não clique ainda em Continuar. Clique antes em Configure Manually, já que precisamos configurar manualmente os servidores de SMTP e POP3 para, respectivamente, enviar e receber mensagens.
Preencha os campos como na imagem a seguir. Detalhe: Não coloque o seu endereço completo com o @mail.i2p, apenas o nome da sua conta.
https://image.nostr.build/4610b0315c0a3b741965d3d7c1e4aff6425a167297e323ba8490f4325f40cdcc.jpg
Clique em Re-test para verificar a integridade da conexão. Se tudo estiver certo uma mensagem irá aparecer avisando que as configurações do servidores estão corretas. Clique em Done assim que estiver pronto para prosseguir.
https://image.nostr.build/8a47bb292f94b0d9d474d4d4a134f8d73afb84ecf1d4c0a7eb6366d46bf3973a.jpg
A seguinte mensagem vai aparecer alertando que não estamos usando criptografia no envio das credenciais. Não há problema nenhum aqui, pois a I2P está garantindo toda a proteção e anonimato dos nossos dados, o que dispensa a necessidade de uso de TLS ou qualquer tecnologia similar nas camadas acima. Marque a opção 'I Understand the risks' e clique em 'Continue'
https://image.nostr.build/9c1bf585248773297d2cb1d9705c1be3bd815e2be85d4342227f1db2f13a9cc6.jpg
E por fim, se tudo ocorreu como devido sua conta será criada com sucesso e você agora será capaz de enviar e receber emails pela I2P usando essa conta.
https://image.nostr.build/8ba7f2c160453c9bfa172fa9a30b642a7ee9ae3eeb9b78b4dc24ce25aa2c7ecc.jpg
## 4. Observações e considerações finais
Como informado pelo próprio site do hq.postman, o domínio @mail.i2p serve apenas para emails enviados dentro da I2P. Emails enviados pela surface devem usar o domínio @i2pmai.org. É imprescindível que você saiba usar o PGP para assinar e criptografar as suas mensagens, dado que provavelmente as mensagens não são armazenadas de forma criptografada enquanto elas estão armazenadas no servidor. Como o protocolo POP3 delete as mensagens no imediato momento em que você as recebe, não há necessidade de fazer qualquer limpeza na sua conta de forma manual.
Por fim, espero que esse tutorial tenha sido útil para vocês. Que seu conhecimento tenha expandido ainda mais com as informações trazidas aqui. Até a próxima.
-

@ fd208ee8:0fd927c1
2024-11-07 07:28:06
## The newspaper barons are all into crypto, now
Watching the outsized-impact we crypto enthusiasts (I'm including Bitcoin in that category), had on the 2024 USA presidential election, was a sobering affair. At the moment, our impact is primarily over the voting box, but, already, indirectly, (over Elon Musik, Donald Trump, and Jack Dorsey, etc.) through our sheer wealth (and the ingenuity that brought us that wealth) being able to influence the voting population, by changing/shifting the communications channels and influencing what is written there.
Elon even reached deep into his foreign-learned bag of political tricks and started [handing out money, directly](https://www.bbc.com/news/articles/crlnjzzk919o), to petition signers.

## Survival of the fittest, ongoing
Now, you all know that I have full respect for an expert player, when I see one, so no hating the hustle, from my side. We all play the hand we are dealt, and the political game is now such a pigsty, that you have to get a bit dirty, to have a chance at winning. Trying to stay neat and above the fray cost Republicans the last election.
It was the most dramatic display of the greatest power following the best money, that has been seen, since the Medici family began minting gold coins. The entire world is in shock. Change is upon us.
He who has the best money, makes the rules.
On a smaller, but not insignificant scale, private wealth and access to Bitcoin funding, have allowed quite a few of us Nostriches, to dedicate time and energy toward promoting and developing the New Internet. Whereas, other people's hobby is increasingly the night shift at the gas station, or doing something mind-numbing, to escape the realities of their current economic misery.
You don't need money to be here, but you can spend more time here, if you have money.
And we are here, writing the rules. We call them NIPs.
## Same ole, same ole
But back to us Bitcoiners...
I increasingly don't see us morally any different than the clever people crowding into any safe asset, during any financial crisis. Like the people who bought agricultural land, gold, and Swiss Francs, before the Reichsmark melted down. The people who had that stuff, mostly managed to keep it, and their children and grandchildren have inherited it. Or they managed to marry back into families, that have done so, by remaining in the same social class, through beauty or talent.

We Bitcoiners have a good narrative to go along with our flight to economic safety, but everyone has that narrative. Humans have a conscience and need to justify their own actions, to themselves. I'm also a goldbug, you see, and a stockholder, and all three assets are rife with the same virtuous narrative.
## How do we save our financial behinds, without being evil?
Some people are simply more situationally aware and have more agency, by nature and circumstances, and they adapt faster. It's not mere intelligence, rather, it also requires a willingness to act and take risks. There's an element of chance to it, but it's still always the same types of people ending up with the assets, with the winners slightly shifting with each round, due to evolution and changes in the environment.
Charity was invented, to get such people to willingly share their assets, or the fruits of their assets, for the common good. So, rather than fret over the morality of the asset, itself, the better response is to consider stepping up your charity (effort or payments), to balance out the inevitable negative impact of the coming _Age of Bitcoin Inequality_.
## Coming down from the ATH
Even now, Bitcoin isn't the only safe asset; it's just the most-fungible and partitionable one, so that it's the one most akin to money. And lines are being blurred, as corporations, funds, governments, and insurers discharge dollars and stock up on harder reserve assets, including Bitcoin.
They can hear the money printers rolling out, already, because nobody can print-n-spend, like Trump can. Let's not forget that the money for the last big bump came from the infamous Trump stimmy checks, that lots of us stacked on crypto.
As Bitcoin flows into such markets, the power will rest with both groups (the direct-hodlers and the title-holders), although the hodlers will initially have the upper hand. I say, _initially_ because many hodlers will need to discharge or invest Bitcoin, to live off of it, but the others don't need to, so it should eventually even out. It could take dozens or even hundreds of years to rebalance. By then, the world will be a very different place, and we don't know if Bitcoin will even still be a part of it.
Assets come, assets go, and I'm just glad I didn't let down my forefathers, by leaving them with the first generation, who failed to adapt. Even if I'm a bit late, to the Bitcoin game, the ball is still in play.
May the best money win.
And may it be mine.
And may I do good with it.
-

@ fd208ee8:0fd927c1
2024-11-07 07:22:14
## Unsucking the feed is real
As a Nostrich with an interesting, thought-provoking, and informative feed... a feed so good, that we're creating clients just to look at that feed... a feed that puts a lie to the idea that Nostr is nothing, but people reposting from Twitter or rehashing worn-out Bitcoin memes... a feed that I personally and increasingly enjoy perusing... I am here to tell you that the feed is real.

It's taken me over a year, to produce this feed. I literally spent hours and hours, day in and day out, scouring the Nostrverse for people worth introducing other people to. It was brutally difficult, as I was fighting the inherent nature of the Nostr clients and relays, in their current, most-popular form.
## It goes like so...
Here are the steps I took, that sometimes weren't possible to take, until I tried to take them, and that still will sometimes break your client because the clients are often _intentionally_ designed to steer you into having one particular feed:
1) **Make a screenshot** of your current relay list and copy your follows list.
2) **Unsubscribe from all the relays**, that you are currently subscribed to. Your feed should disappear. If it doesn't, or it doesn't allow for this, switch to a different client app because yours is corrupted.
3) **Unfollow everyone.** Delete the whole list. You are taking your follows private, which will invariably result in only following npubs whose stuff you actually want to see, since there's no longer any virtue-signaling going on. Also, it's easier to explain having no list, than a very short one. If your client doesn't allow for this, or starts throwing error messages and freezing up, then switch to a different client app because yours is corrupted.
4) **Curate your copied follows list.** Go line by line and look at the feed produced by the npub on that list.
* Do you want to see that in your feed, going forward?
* Do they produce original content and/or are they interesting conversationalists, in the replies?
* Have they been active, within the past three months?
* Are they simply good friends or real-life acquaintances, that you want to keep tabs on?
* If not, cross out their name.
* If you have been following someone because they repost or quote interesting things, **look at who they've been reposting** and follow them, instead.
5) Of the npubs remaining on your list, go through and select the 10 most interesting ones, and **look at the reposts and quotes** in their feed, and their topical lists like \"Favorites\", \"Devs\", \"Recipes\", etc. (Not their follows list, unless it's quite short, as follows tend to be full of people they follow for social-signaling or client-functional reasons, that they don't actively look at.) Find some new follows, there.
6) Now, set up a personal relay and add all the follows, that made the cut, to **your allowed-npubs list**. Do not add people to the list, just to make them feel better, or because you feel guilty, as they follow you, or to keep them from yelling at you. Remember, they can't see the list!
7) Think about the topics you find interesting, and add an **allowed-keywords list** (this is better than hashtags, as it searches the entire content of the notes), with the OR operator (these allowed npubs OR these allowed topics).
8) Make sure that you choose words likely to find the content you are most-interested in, and not people just ranting about it or spamming (those are great additions to your relay's block-list). If you are Muslim, for instance, instead of "Islam" or "shariah", choose "hadith" or "riba", as those are words more-likely to be used by people who know what they are talking about. If you are into bread baking, add "sourdough", "rye", "yeast", or "whisk", but don't add "bread" or "carbs". Once a note from those people shows up in your feed, and their feed looks like someone interesting, you can add their npub to your allow list. Remember: **The topics are there to find people to add to the allow list**, not merely for their own sake, as this is not a topical relay, but a personal one.
9) Open up a faucet (or relay syncing) with some of the big relays you previously unsubscribed from, some WoT relays, and some of the paid relays (nostr.land, nostr.wine, nostr21.com, and sovbit.host, for example). **Your relay will filter that feed** and only accept the events from the people and topics on your list. As your relay becomes more popular, npubs will begin writing directly to it, and the connections to other relays will sink in significance.
10) Go to your client of choice and **subscribe to your new relay**. Also subscribe to some topical relays, or curated neighborhood relays, you find interesting or your frens are running. This is an easy way to find new, interesting npubs, to add to your own relay.

That's a lot of work, you say? Yes, but the result is great, and you are now fully in-charge of your own feed. You also -- here's the cool part -- have a feed good enough, that other people can add your feed to theirs and enjoy your manual curation. As you refine and expand your feed, theirs will also be refined, in parallel. You are now an official Nostr Community Curator. My sincere congratulations.
## Why is this so hard?
This is only a lot of work because the clients aren't designed to interact with relays, to this extent, as they were created to service mega-relays, download all their crap to your local cache, and adjust the feed over the follows/mutes lists. This was an idea borne of the axiom that Relays Are Hard, so there will only ever be a handful of them, where we'd all clump together and the relay operators would never judge the quality of someone's content. Then, some unusually clever people made relays increasingly easy, and the mailbox communication model was invented, and here we are.
What we have now, and that is slowly growing in popularity, among the #NostrIntelligentsia, are Nostr clients aimed at curating and viewing individual relays or personalized sets of smaller or more-specialized relays. The reigning client devs refused to give us those clients, and most of us aren't up to developing our own clients, so the relay devs took matters into their own hands and made the clients themselves. The free market remains undefeated.
This is a total game-changer. Last one to board this train is a rotten egg.
Originally, relays were supposed to be completely stupid and clients were supposed to be completely smart, but it's now actually the other way around, because most relay devs have a market-born incentive to make their content highly customizable and appealing to individuals (so that more people run relays).
## But what about algos?
Can't you just slap an algo on top of Damus, Lol, or Primal relays, and get the same result? I would argue... no. No, you can't. Or, rather, only in the short to medium term.
Running your own relay, is running your own server. You are now _intellectually independent_, at a machine-level, and therefore a fully sovereign consumer. If you then use algos to control your own server, or in a client that subscribes to your own server, then you can further-refine a feed that is already in a high-to-you-signal state, rather than risking an algo inching you toward the Consensus Feed.
I have noticed that my own feed is slowly drifting away from the ReplyGuy-Cryptobot-Porny-Bitcoin-Meme Dumpster Fire, that almost everyone else is looking at, and it's due to running my own relay. If I use DVMs, those algos sometimes refer to relays I intentionally avoid, so they return results according to those relays. The results are as underwhelming, as you would expect, and often are simply 31 flavors of the Trending List.
But, that isn't your problem, anymore.
From here, you can actively expand and refine your feed, over your whitelist, the topics, and your personally-managed algos.
Happy Nostr-ing!
-

@ f462d21e:1390b6b1
2024-11-07 03:52:04
eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyIsImZlZWRiYWNrIjp7ImZlZWRiYWNrIjowLCJwYWdlciI6eyJ0b3RhbEl0ZW1zIjowfSwibWVzc2FnZSI6Im5vIHJlc3VsdHMgZm91bmQifX0=
-

@ f462d21e:1390b6b1
2024-11-06 04:39:14
eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9
-

@ f462d21e:1390b6b1
2024-11-06 04:19:42
eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9
-

@ f462d21e:1390b6b1
2024-11-06 04:14:05
eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9
-

@ a367f9eb:0633efea
2024-11-05 08:48:41
Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The [reporting](https://www.reuters.com/technology/artificial-intelligence/chinese-researchers-develop-ai-model-military-use-back-metas-llama-2024-11-01/) purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
> In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
>
> The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history?
As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times.
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
Open-source matters When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
Open-source is for your friends, and enemies In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
Limiting open-source threatens our own advancement If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols.
The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
> In a June paper reviewed by[ Reuters](https://www.reuters.com/technology/artificial-intelligence/chinese-researchers-develop-ai-model-military-use-back-metas-llama-2024-11-01/), six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
>
> The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the *Star Trek* episode “[A Taste of Armageddon](https://en.wikipedia.org/wiki/A_Taste_of_Armageddon)“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over [one million open-source LLMs](https://huggingface.co/models) available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are [potentially](https://bigthink.com/business/the-trillion-dollar-ai-race-to-create-digital-god/) trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American[ infrastructure](https://www.nbcnews.com/tech/security/chinese-hackers-cisa-cyber-5-years-us-infrastructure-attack-rcna137706),[ data](https://www.cnn.com/2024/10/05/politics/chinese-hackers-us-telecoms/index.html), and yes, [your credit history](https://thespectator.com/topic/chinese-communist-party-credit-history-equifax/)?
**As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much[ many times](https://consumerchoicecenter.org/made-in-china-sold-in-china/).**
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
## **Open-source matters**
When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various [licensing schemes](https://opensource.org/licenses) – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also [open-source](https://github.com/bitcoin), which has allowed [thousands](https://bitcoinmagazine.com/business/bitcoin-is-money-for-enemies) of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
## **Open-source is for your friends, and enemies**
In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to[ Hugging Face](https://huggingface.co/), download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put [export controls](https://www.reuters.com/technology/us-lawmakers-unveil-bill-make-it-easier-restrict-exports-ai-models-2024-05-10/) on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see[ The Crypto Wars](https://en.wikipedia.org/wiki/Export_of_cryptography_from_the_United_States)). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
## **Limiting open-source threatens our own advancement**
If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “[Hundred Year Marathon](https://www.amazon.com/Hundred-Year-Marathon-Strategy-Replace-Superpower/dp/1250081343)” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with [trillions of dollars’](https://www.economist.com/china/2024/11/04/in-some-areas-of-military-strength-china-has-surpassed-america) worth of investments that span far beyond AI chatbots and skip logic protocols.
The [theft](https://www.technologyreview.com/2023/06/20/1075088/chinese-amazon-seller-counterfeit-lawsuit/) of intellectual property at factories in Shenzhen, or in US courts by [third-party litigation funding](https://nationalinterest.org/blog/techland/litigation-finance-exposes-our-judicial-system-foreign-exploitation-210207) coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
*Originally published on the website of the [Consumer Choice Center](https://consumerchoicecenter.org/open-source-is-for-everyone-even-your-adversaries/).*
-

@ a10260a2:caa23e3e
2024-11-05 06:21:10
TIL Google Authenticator can potentially collect a lot of data, more than some of the other popular 2FA apps[^1].
[^1]: https://www.pcmag.com/reviews/google-authenticator
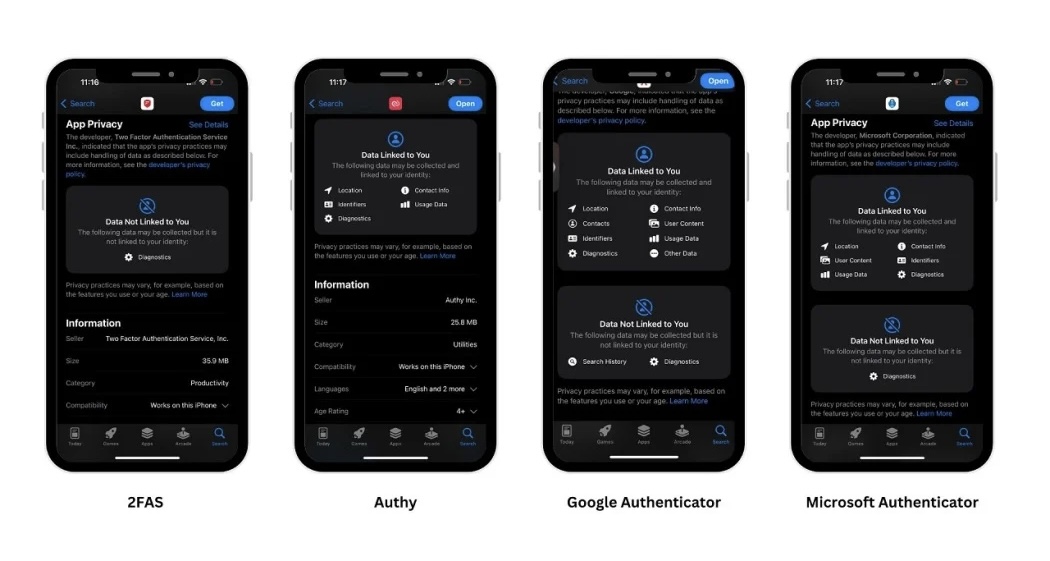
Whether it does or it doesn’t, if you’re like me, you don’t turn down an opportunity to remove some Google from your life and add in some open-source.
Here’s a quick overview of the migration process.
**Step 1: Download [2FAS](https://apps.apple.com/us/app/2fa-authenticator-2fas/id1217793794)**
**Step 2: Export accounts from Authenticator**
This can be done via “Transfer accounts” in the sidebar. If you’re transferring on the same phone, take a screenshot of the QR code.
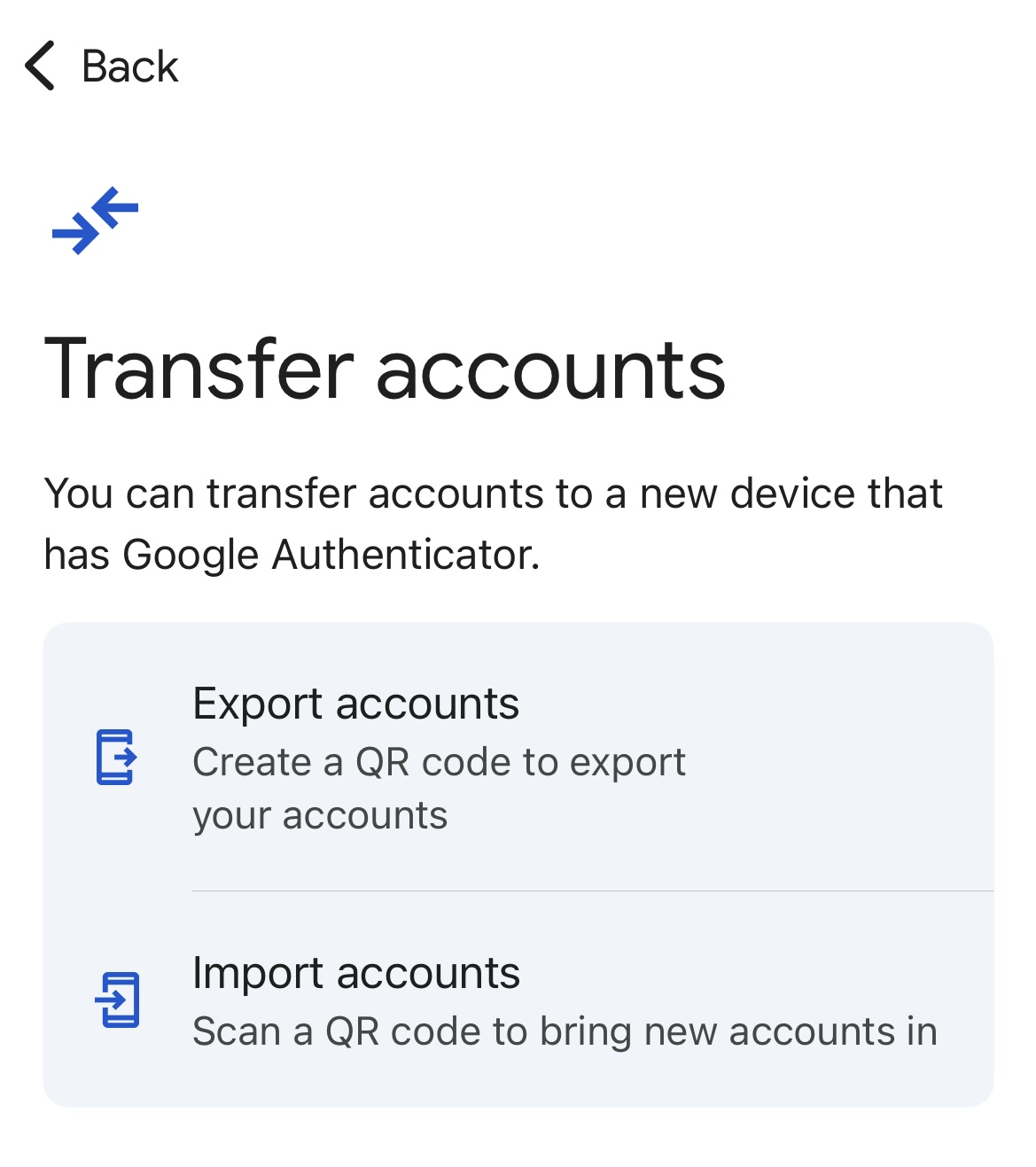
**Step 3: Import accounts into 2FAS**
During the setup process for 2FAS, you’ll be given the option to import existing tokens from Google. This is where you’ll tap “Choose QR Code” and select the screenshot you took in step 2.
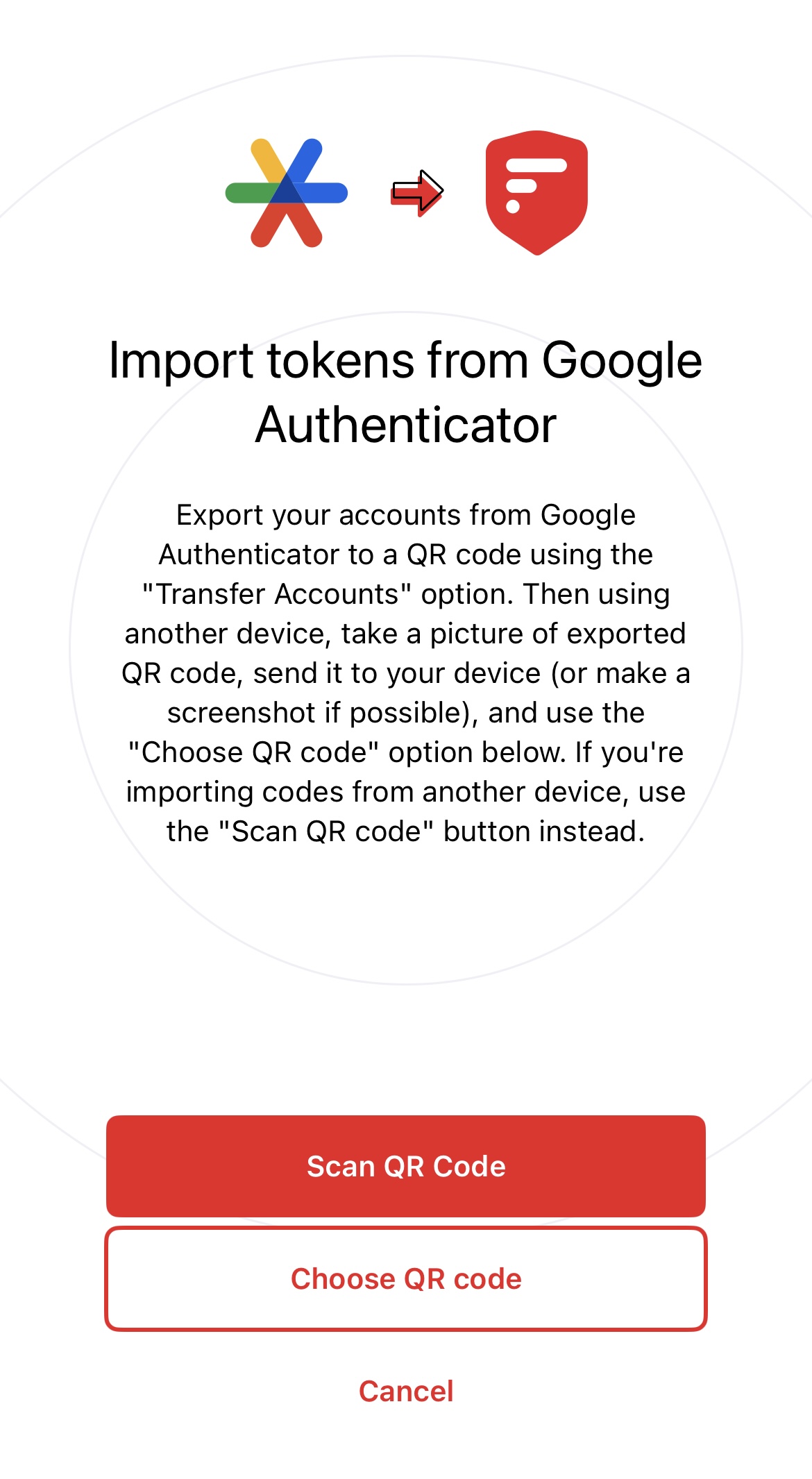
Note that when you tap continue after importing the tokens, you’ll be taken back to the same screen as above. I think it should take you to your list of accounts after. Either way, don’t think the import failed. Just tap cancel, and you’ll be taken there.
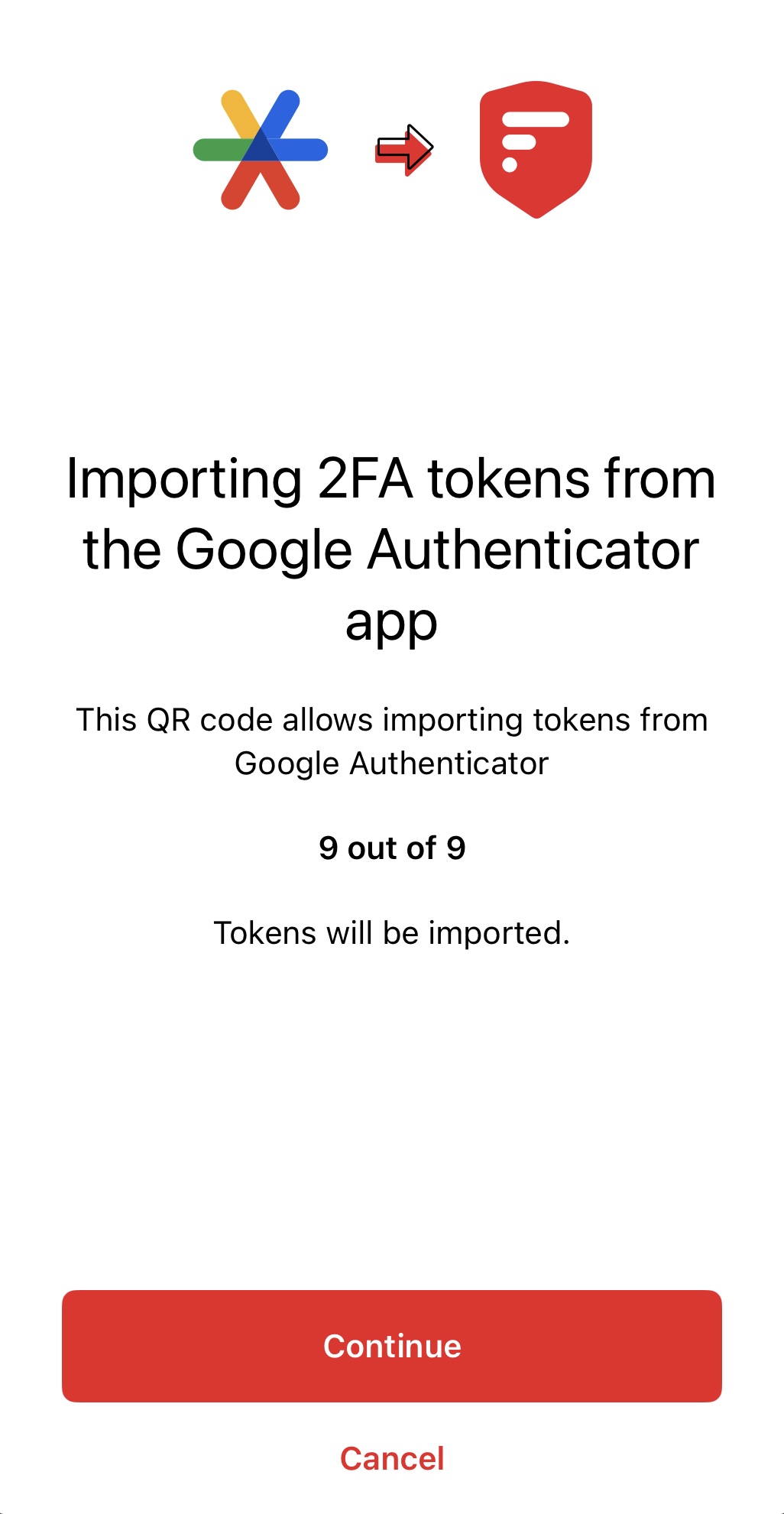
If you’re on Android, check out [Aegis](https://github.com/beemdevelopment/Aegis). 🫡
originally posted at https://stacker.news/items/753472
-

@ 472f440f:5669301e
2024-11-05 04:24:47
All eyes are, unsurprisingly, on the US Presidential election. Tomorrow is the big day. I don't want to come off as preachy, however it is pretty clear to me that if you are an American citizen who cares about bitcoin and would like to live under an administration that is eager to embrace the industry as opposed to an administration that is actively hostile toward bitcoin there is only one candidate who deserves your vote; Donald J. Trump. I think he's a better candidate for other reasons, but if you've read this rag for long enough you probably already know what those are. Instead of writing a screed about why I am voting for Trump, let's highlight some things outside of the election that you should be paying attention to this week.
First up, there are two Treasury auctions; $42B of 10-Year notes tomorrow and $25B 30-Year bonds on Wednesday.
It will be interesting to see what the demand for these auctions is and how they affect rates. The long end of the yield curve has been pumping since the Fed's rate cut in the middle of September, which is the market signaling that it does not believe inflation has been appropriately tamed. Yields came down today, but as you can see from the charts things are trending in the wrong direction.
As the Treasury issues new debt at higher rates, the interest expense on that debt, naturally, drifts higher. If the long end of the yield curve doesn't come down aggressively over the course of the next year this is going to be a big problem. There are trillions of dollars worth of Treasury debt that needs the be rolled over in the next few years and it would be advantageous for the Treasury if that debt wasn't being rolled over with yields as high as they are. With the amount of debt the country has accrued in recent decades, every incremental dollar of debt that gets issued and/or rolled over at higher interest rates exacerbates the problem. We are approaching the territory of runaway exponentials, as evidenced by this chart.
The growth slope gets steeper and steeper
This debt problem is the elephant in the room that needs to be addressed as quickly as possible. The national debt hit $1.2T in early 1983. It then took 26 years to 10x from $1.2T to $12T in late 2009 and has only taken another 15 years to triple from there to $36T or 30x from the arbitrary base I picked out (Q1 1983).
With this in mind, keep an eye out for these auctions tomorrow and Wednesday, where rates end at the end of trading on Wednesday, and whether or not we officially push over $36T. Regardless of who wins the election tomorrow, this is a problem that needs to be confronted. Whether or not it can be solved at all is up for debate. I don't see how what can be done to reel in this runaway train at this point. However, at the very least, we should acknowledge that we're in the realm of exponentials and have people prepare accordingly by accumulating hard assets that cannot be debased (bitcoin).
The other thing to pay attention to is the FOMC meeting on Wednesday and the announcement of the results of the meeting on Thursday. Will Jerome and the other Fed board members to keep rates where they are, cut, or raise rates? Raising rates seems to be out of the question despite the fact that many believe it would be the most prudent move considering how the long end of the yield curve reacted to the 50bps cut in September. If they decide to cut rates, by how much will they cut them? Will they slow the pace with a 25bps cut or continue at the 50bps clip established in September?
We'll find toward the end of this week. Don't lose sight of these events while the world is enthralled with the elections in the US.
I don't know about you freaks, but I couldn't feel more fortunate that bitcoin exists at a time like this. Having access to a distributed peer-to-peer digital cash system with a fixed supply during a time of incredible political divisiveness and out-of-control runaway sovereign debt feels like a Godsend.
Stay sane out there.
Final thought...
We're going to win.
-

@ fd208ee8:0fd927c1
2024-11-03 21:51:39
## All memed out
It finally happened. I think it was October 25th, at circa 18:45 in the evening. I was doomscrolling my Nostr feed, and kept seeing the same Bitcoin memes repeated over and over, by different people. They weren't even reposts, they were copy-pasted versions of the same image. A very funny image. Well, it was very funny last year... and the year before that... and probably the year before that, when it appeared on a different network.
Because it's all just reposts, copy-pastes and rehashes of the Best of Bitcoin Twitter, just like the tiresome influencers, with their groupies and their Episode 498 of *Let's all eat a large chunk of lightly-burnt dead animal and count our stacks before jetting off to talk about how to save the poors by getting them to buy individual satoshis with money they don't have*.

## I'm the poors your looking for
It's all so tiresome. It has little bearing on the real world I see around me, where most people are thinking all day about 99 problems and Bitcoin ain't one.
Which is, of course, what the Bitcoin influencers would have you believe, is the reason that they're poor. What in the world could be more important, than thinking about Bitcoin? Why do these people not get with the program? Don't they know, that we are trying to save them?
Why are they worrying about OtherProblems? Don't they know that all OtherProblems can be fixed with Bitcoin? Really, if you just go back far enough, in any current, situational problem, you will discover that there was some slight, negative shift to the history record that involved soft money. It's the financial version of the Butterfly Effect.
That's why #BitcoinFixesThis. Bitcoin fixes everything, if you just think about it, for long enough.
The same way that we all actually come out of Africa, supposedly, if you go back enough generations. So, coming out of Africa, now, as a Real Life Person in The Present is supposed to have no significance. What does someone from Cameroon know about Africa, that someone from Alaska doesn't? Both people come out of Africa, if you just think about it, for long enough.

And maybe that really is true. Maybe Bitcoin will eventually end all vice and crimes, save the planet, and we will all just hold hands and sing kumbaya all day, while waiting for the Singularity to upload us to Satoshi.
## Bitcoin envelope budgeting
Or maybe it's not. Maybe it's just a really hard, digital money that incentivizes savings, functions as a reliable measure, and makes micropayments possible on a global scale. Those really are things that will help the poors, including myself. I can see it, already, when trying to organize pre-paid meetups or figure out what to do with our household's meager savings, when the stock market is looking particularly bubblicious.

But this is what I would consider Boring Bitcoin. Bitcoin home economics. Penny-pinching Bitcoin. Bitcoin for homemakers. How to use the Bitcoin envelope budgeting system to beat inflation by a margin of 13%.
The actual use of Bitcoin as money, rather than as a mere investment gamble or hype machine. That's the part of Bitcoin that nobody seems to really talk about because it's incredibly practical, dull, and useful, and it can only be tested by -- Oh, the horror! -- actually spending Bitcoin.
But... perhaps I will begin talking about it. Perhaps those of us, Bitcoiners, who are having fun staying poor, while stacking sats, should speak up a bit more. Perhaps the boring stuff is actually the interesting stuff. Perhaps there is more to say about Bitcoin, than can fit into a meme.
-

@ fd208ee8:0fd927c1
2024-11-03 12:01:43
## It arrived!
I was feeling impatient, waiting for my snazzy, brand-spanking new mobile phone to arrive, but when it got here, I just stared at the box, in trepidation. Everyone kept walking by, asking how it is, but I just shook my head. After nearly four years, with my (originally Android 10), Moto G8 Power, which I loved to death, I wasn't yet ready to move on. I needed a moment, to grieve.
RIP, my trusty fren.

## Anyways...
Around 10 pm, I managed to emotionally recover enough to begin the Big Transition, and I was up until 2 am, and still didn't finish.
My **SimpleX** database is sort of large, and slow to migrate. Also, took me a while to figure out how to do it, and the whole thing made me terribly nervous, that I'd accidentally get locked out. But it worked, after eight failed attempts, so yay.
**Telegram** was back online, almost immediately, since it's tied to the SIM card. Which was convenient, but sorta creeped me out.
Our family-internal favorite, **Threema**, was a snap. Took 5 minutes.
I had four failed starts with **Slack**, as it kept sending a login code to my Proton Mail, but I didn't have Proton app installed on my new phone, yet, and I was really sleepy, so I kept confirming on the old phone and then Slack would freeze up, and I had to kill the process and restart.
My **key manager** is cloud-based, so that went really fast, and I had the nos2x browser extension going in Firefox within 10 minutes, or so. Logged into Habla.News, Nostr.Build, Zap.Cooking, and Nostrudel.Ninja, immediately, so that I can get my Nostr fix.
Then I took a deep breath and mass-installed F-Droid, Minibits, **Amethyst**, Citrine, Orbot, and Amber. And breathed out, again, because MIRACLES NEVER CEASE: it seems to be actually working.
Everyone knows that this is the unbeatable Android Nostr setup, but it's also a resource-gobbling monster, that should only be tried at home, kids. Make sure you don't use Amethyst when out-and-about, unless you have a gigantic battery and an unlimited, high-speed, mobile plan. So, basically, everyone in the First World, who isn't me, can do it.
Oh, well. At least, I can now indulge over WiFi.
The phone itself is just like the old one, but thinner, faster, and doesn't freeze up or take a long time to start. The Motorola is dead. Long live the Motorola.
-

@ fd208ee8:0fd927c1
2024-11-03 09:20:33
# It's that season, again
I've been growing my hair out (too lazy to cut it) and it has -- once again -- quickly reached a length at which it draws unnecessary attention and sheds everywhere. I suppose it always sheds everywhere, but shedding short hairs is just generally less-gross than finding a 12-inch strand lying on the toast, you were about to consume.
So, I'm back to the _50 Shades of Updo_ stage, where I struggle to figure out how to best wear my head, usually defaulting to the _Messy Bun_ look, because it's still too short to do anything more elaborate and looks silly, as a ponytail.


It's really not that great of a look for me, I know, especially, now that my chin is finally succumbing to gravity, but doing something more-elegant is usually more time-consuming and doesn't have that wonderful "swept up" feeling to it. You know that feeling, when you tie all of that heavy hair to a higher point on your skull and the roots just sigh with relief.
Another look, I tend to gravitate toward, at the moment, is head scarves, like this one:

...or a Bavarian-style bandana, for gardening or hiking (don't have a selfie handy, so here is some random chick, who also suffers from poofy, dark hair).

Hiking bare-headed, with flowing tresses, is not recommended, due to all of the Nature, that you have to comb back out of it.
Generally, just bored of my inbetween length and looking forward to braiding it, in a few months. Or giving up, in frustration, and cutting it all off.
-

@ 09fbf8f3:fa3d60f0
2024-11-02 08:00:29
> ### 第三方API合集:
---
免责申明:
在此推荐的 OpenAI API Key 由第三方代理商提供,所以我们不对 API Key 的 有效性 和 安全性 负责,请你自行承担购买和使用 API Key 的风险。
| 服务商 | 特性说明 | Proxy 代理地址 | 链接 |
| --- | --- | --- | --- |
| AiHubMix | 使用 OpenAI 企业接口,全站模型价格为官方 86 折(含 GPT-4 )| https://aihubmix.com/v1 | [官网](https://aihubmix.com?aff=mPS7) |
| OpenAI-HK | OpenAI的API官方计费模式为,按每次API请求内容和返回内容tokens长度来定价。每个模型具有不同的计价方式,以每1,000个tokens消耗为单位定价。其中1,000个tokens约为750个英文单词(约400汉字)| https://api.openai-hk.com/ | [官网](https://openai-hk.com/?i=45878) |
| CloseAI | CloseAI是国内规模最大的商用级OpenAI代理平台,也是国内第一家专业OpenAI中转服务,定位于企业级商用需求,面向企业客户的线上服务提供高质量稳定的官方OpenAI API 中转代理,是百余家企业和多家科研机构的专用合作平台。 | https://api.openai-proxy.org | [官网](https://www.closeai-asia.com/) |
| OpenAI-SB | 需要配合Telegram 获取api key | https://api.openai-sb.com | [官网](https://www.openai-sb.com/) |
` 持续更新。。。`
---
### 推广:
访问不了openai,去`低调云`购买VPN。
官网:https://didiaocloud.xyz
邀请码:`w9AjVJit`
价格低至1元。
-

@ f462d21e:1390b6b1
2024-11-02 05:29:26
eyJfaWQiOiIwMjkwMWQ4Yi04YWFhLTRiMTYtYWZhOS0wMTMzMGY4MTI4YzEiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX0JVWSIsImNvdW50cnkiOiJGcmFuY2UiLCJjb3VudHJ5Q29kZSI6IkZSIiwibGF0IjpudWxsLCJsb24iOm51bGwsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiQ1JZUFRPQ1VSUkVOQ1kiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJtYXJrZXRQcmljZSI6bnVsbCwiZml4ZWRQcmljZSI6MTQ5LCJidXllclNldHRsZW1lbnRBZGRyZXNzIjoiODg4dE5rWnJQTjZKc0VnZWtqTW5BQlU0VEJ6YzJEdDI5RVBBdmtSeGJBTnNBbmp5UGJiM2lRMVlCUmsxVVhjZFJzaUtjOWRod01WZ041UzljUVVpeW9vZ0RhdnVwM0giLCJtaW5BbW91bnQiOjIwMCwibWF4QW1vdW50IjoyMDAwLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCBjcnlwdG8gdHJhZGVyIiwibXNnIjoic2NhbW1lcnMgaGF2ZSBubyBjaGFuY2UuIHByb2l2ZGUgYmxvY2tjaGFpbiBsaW5rIGFmdGVyIHBheW1lbnQiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInJlcXVpcmVGZWVkYmFja1Njb3JlIjpudWxsLCJmaXJzdFRpbWVMaW1pdEFzc2V0IjpudWxsLCJwYXltZW50V2luZG93TWludXRlcyI6NjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDJUMDU6Mjk6MjYuNzQ1WiJ9
-

@ f462d21e:1390b6b1
2024-11-01 22:45:56
deleted
-

@ a95c6243:d345522c
2024-11-01 18:22:43
*Die «moralische Weltordnung» – eine Art Astrologie.
Friedrich Nietzsche*
**Das Treffen der BRICS-Staaten beim [Gipfel](https://transition-news.org/brics-gipfel-in-kasan-warum-schweigt-die-schweiz) im russischen Kasan** war sicher nicht irgendein politisches Event. Gastgeber Wladimir Putin habe «Hof gehalten», sagen die Einen, China und Russland hätten ihre Vorstellung einer multipolaren Weltordnung zelebriert, schreiben Andere.
**In jedem Fall zeigt die Anwesenheit von über 30 Delegationen aus der ganzen Welt,** dass von einer geostrategischen Isolation Russlands wohl keine Rede sein kann. Darüber hinaus haben sowohl die Anreise von UN-Generalsekretär António Guterres als auch die Meldungen und Dementis bezüglich der Beitrittsbemühungen des NATO-Staats [Türkei](https://transition-news.org/turkei-entlarvt-fake-news-von-bild-uber-indiens-angebliches-veto-gegen-den) für etwas Aufsehen gesorgt.
**Im Spannungsfeld geopolitischer und wirtschaftlicher Umbrüche** zeigt die neue Allianz zunehmendes Selbstbewusstsein. In Sachen gemeinsamer Finanzpolitik schmiedet man interessante Pläne. Größere Unabhängigkeit von der US-dominierten Finanzordnung ist dabei ein wichtiges Ziel.
**Beim BRICS-Wirtschaftsforum in Moskau, wenige Tage vor dem Gipfel,** zählte ein nachhaltiges System für Finanzabrechnungen und Zahlungsdienste zu den vorrangigen Themen. Während dieses Treffens ging der russische Staatsfonds eine Partnerschaft mit dem Rechenzentrumsbetreiber BitRiver ein, um [Bitcoin](https://www.forbes.com/sites/digital-assets/2024/10/23/russia-launches-brics-mining-infrastructure-project/)-Mining-Anlagen für die BRICS-Länder zu errichten.
**Die Initiative könnte ein Schritt sein, Bitcoin und andere Kryptowährungen** als Alternativen zu traditionellen Finanzsystemen zu etablieren. Das Projekt könnte dazu führen, dass die BRICS-Staaten den globalen Handel in Bitcoin abwickeln. Vor dem Hintergrund der Diskussionen über eine «BRICS-Währung» wäre dies eine Alternative zu dem ursprünglich angedachten Korb lokaler Währungen und zu goldgedeckten Währungen sowie eine mögliche Ergänzung zum Zahlungssystem [BRICS Pay](https://en.wikipedia.org/wiki/BRICS_PAY).
**Dient der Bitcoin also der Entdollarisierung?** Oder droht er inzwischen, zum Gegenstand geopolitischer [Machtspielchen](https://legitim.ch/es-ist-ein-sieg-fuer-bitcoin-waehrend-russland-und-die-usa-um-die-krypto-vorherrschaft-kaempfen/) zu werden? Angesichts der globalen Vernetzungen ist es oft schwer zu durchschauen, «was eine Show ist und was im Hintergrund von anderen Strippenziehern insgeheim gesteuert wird». Sicher können Strukturen wie Bitcoin auch so genutzt werden, dass sie den Herrschenden dienlich sind. Aber die Grundeigenschaft des dezentralisierten, unzensierbaren Peer-to-Peer Zahlungsnetzwerks ist ihm schließlich nicht zu nehmen.
**Wenn es nach der EZB oder dem IWF geht, dann scheint statt Instrumentalisierung** momentan eher der Kampf gegen Kryptowährungen angesagt. Jürgen Schaaf, Senior Manager bei der Europäischen Zentralbank, hat jedenfalls dazu aufgerufen, [Bitcoin «zu eliminieren»](https://www.btc-echo.de/schlagzeilen/ezb-banker-es-gibt-gute-gruende-bitcoin-zu-eliminieren-194015/). Der Internationale Währungsfonds forderte El Salvador, das Bitcoin 2021 als gesetzliches Zahlungsmittel eingeführt hat, kürzlich zu [begrenzenden Maßnahmen](https://legitim.ch/el-salvador-iwf-fordert-trotz-nicht-eingetretener-risiken-neue-massnahmen-gegen-bitcoin/) gegen das Kryptogeld auf.
**Dass die BRICS-Staaten ein freiheitliches Ansinnen im Kopf haben,** wenn sie Kryptowährungen ins Spiel bringen, darf indes auch bezweifelt werden. Im [Abschlussdokument](http://static.kremlin.ru/media/events/files/en/RosOySvLzGaJtmx2wYFv0lN4NSPZploG.pdf) bekennen sich die Gipfel-Teilnehmer ausdrücklich zur UN, ihren Programmen und ihrer «Agenda 2030». Ernst Wolff nennt das «eine [Bankrotterklärung](https://x.com/wolff_ernst/status/1849781982961557771) korrupter Politiker, die sich dem digital-finanziellen Komplex zu 100 Prozent unterwerfen».
---
Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/aufstand-gegen-die-dollar-hegemonie)* erschienen.
-

@ c69b71dc:426ba763
2024-10-31 16:02:10
# Risks and Regulations
### Food contact materials (FCMs)
Materials that come into contact with food during processing, packaging, or transport – play a critical role in food safety. However, chemicals can migrate from these materials into food, introducing potential health risks.
For instance, chemicals can leach into food from packaging materials, especially during microwaving, pasteurization, or other high-temperature exposures. Even printing inks on the outer packaging, if not well-contained, can migrate into the food or drink. Factors like high temperatures, small package-to-food ratios, fatty foods, and long storage times all increase this risk.
More than 12,200 chemicals have been identified in FCMs, but only about 100 substances are regulated by the European Union, focusing mainly on plastics. The actual composition of many materials is often undisclosed due to proprietary protection, making it challenging to assess risks fully. Even less is known about secondary substances, which may arise from additives breaking down during manufacturing.

> In 2016, EU regulation defined publicly that *current regulations do not sufficiently protect public health from the harmful impacts of chemicals migrating from food packaging.* The current paradigm for evaluating the safety of FCMs is insufficient, as there is a general underestimation of the role of FCMs in food contamination and a lack of information on human exposure. FCMs are a significant source of human exposure to chemicals of concern, including perfluorinated compounds (PFCs) and endocrine-disrupting chemicals (EDCs), as well as those linked to neurodevelopmental issues.
Moreover, the legal framework doesn’t account for the cumulative "cocktail effect" of multiple low-level chemical exposures, which can collectively exceed safe limits. Research shows that FCMs can contribute to serious health issues like cardiovascular disease, diabetes, obesity, neurological disorders, and cancer.
Although packaging is designed to preserve food, maintain quality, and extend shelf life, its chemical impacts remain insufficiently regulated, posing risks that demand greater transparency and robust oversight.
### So what can we do?
Be mindful and use less packaged food. Plastic is sometimes even less harmful than paper, as many chemicals and synthetic materials are used in paper production to improve texture and prevent humidity from transferring through the paper packaging. Additionally, the barrier between ink and food in paper packaging is often not very effective.
Chemicals are mostly invisible...!

-

@ cf5b8c65:494a0912
2024-10-31 11:55:39
Estoy probando un plugin para Obisidian que permite publicar directamente en NOSTR los artículos que has creado en Obsidian.
-

@ fd208ee8:0fd927c1
2024-10-31 11:03:08
## Chef's notes
I got the recipe from the [byanjushka website](https://byanjushka.com/erdnussbutter-kekse-rezept-8177/). She includes a lot more information on there, and lots of pictures and instructions. But it's all in German, so here's my quickie, English version. I've doubled the amounts, as I first baked this for the #PurpleKonnektiv meetup, and I knew I'd have some hungry guests.
The cookies are vegan, but they're mostly just peanut, so it's sort of irrelevant. Just make sure you get the really high-quality peanut butter that is 100% peanut. You can usually identify it by the fact that the oil separates from the base, a bit. Everything else is probably with hardened palm oil, or something.
## Details
- ⏲️ Prep time: 15 min
- 🍳 Cook time: 10 min
- 🍽️ Servings: 30 cookies
## Ingredients
- 500 g peanut butter, normal or crunchy
- 300 g brown (or raw) sugar
- 160 ml plant-based milk (or cows' milk, if you don't care about vegan)
- 1 pkg vanilla sugar (bourbon is nice) or 1 tsp vanilla
- 250 g flour
- 2 tsp baking powder
- 2/3 tsp salt
## Directions
1. Preheat oven to 180 °C (350 °F).
2. Beat together the peanut butter and the sugars, with an electric mixer.
3. Mix in milk and vanilla.
4. In a separate bowl, stir together flour, salt, and baking powder.
5. Stir the dry ingredients into the wet ingredients, and then knead the dough a bit.
6. (At this point, I put the dough in the fridge overnight, and baked it the next day.)
7. Line your baking sheet with baking paper.
8. Form tbsp-spoon-sized balls of dough.
9. Press each one flat, with a fork, dipping the fork in water, before each press (to keep the dough from sticking to the fork).
-

@ eac63075:b4988b48
2024-10-30 20:58:01
Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions.
https://www.fountain.fm/episode/hVVS7hrsX8VQ9SPoUYbg
## What Are Cryptocurrencies?
Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably.
## The Origin of the Myth: Cryptocurrencies and Illicit Activities
The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use.
## Current Data: Cryptocurrencies and Illicit Activities
[According to the **2024 Cryptocurrency Crime Report** from **Chainalysis**](https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/?ref=eddieoz.com), only **0.34%** of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities.
## Comparison with Traditional Money
When we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. [According to a report by **Verafin**](https://verafin.com/2024/02/a-3-1-trillion-financial-crime-epidemic/?ref=eddieoz.com), about **3.1 trillion dollars** are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately **3.87%** of all money in circulation.
In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies.
## The Transparency of Blockchain
One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record.
Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace.
## How Much Money Is There in the World?
To understand the scale, it’s interesting to know that, according to the **World Population Review**, [about **80 trillion dollars** are in circulation globally](https://worldpopulationreview.com/metrics/how-much-money-is-in-the-world?ref=eddieoz.com), including physical and digital money. Out of this total, only **5 trillion dollars** is in physical cash. This shows that most transactions are already digital, even in the traditional financial system.
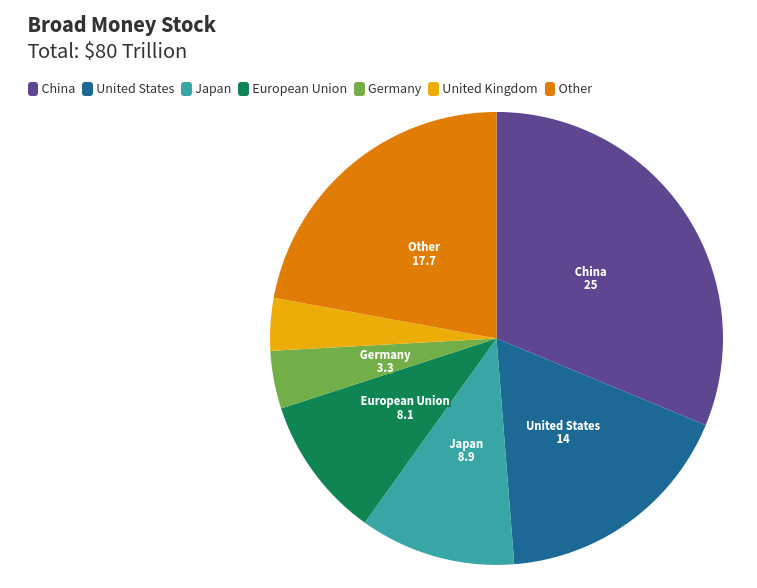## Cryptocurrencies Promote Economic Freedom
Cryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services.
This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them.
## Myths and Realities
It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation.
## Conclusion: Are Cryptocurrencies Really the Villains?
The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception.
If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause.
## And You, What Do You Think?
Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion!Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions.
What Are Cryptocurrencies? Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably.
The Origin of the Myth: Cryptocurrencies and Illicit Activities The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use.
Current Data: Cryptocurrencies and Illicit Activities According to the 2024 Cryptocurrency Crime Report from Chainalysis, only 0.34% of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities.
Comparison with Traditional Money When we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. According to a report by Verafin, about 3.1 trillion dollars are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately 3.87% of all money in circulation.
In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies.
The Transparency of Blockchain One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record.
Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace.
How Much Money Is There in the World? To understand the scale, it’s interesting to know that, according to the World Population Review, about 80 trillion dollars are in circulation globally, including physical and digital money. Out of this total, only 5 trillion dollars is in physical cash. This shows that most transactions are already digital, even in the traditional financial system.
Cryptocurrencies Promote Economic Freedom Cryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services.
This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them.
Myths and Realities It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation.
Conclusion: Are Cryptocurrencies Really the Villains? The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception.
If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause.
And You, What Do You Think? Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion!
-

@ 8f69ac99:4f92f5fd
2024-10-30 14:54:26
Nos últimos anos, a narrativa dominante retrata a mineração de Bitcoin como um consumidor voraz de energia, com impactos ambientais desproporcionais. Embora a mineração de Bitcoin exija uma quantidade significativa de energia, esta visão ignora um ponto crucial: o seu potencial para promover a sustentabilidade ambiental e remodelar a integração de energias renováveis.
Este artigo vai além dos debates convencionais sobre a pegada de carbono, explorando como a mineração de Bitcoin pode mitigar os impactos ambientais e catalisar uma transição energética sustentável, transformando o que alguns consideram uma inutilidade num aliado contra a dependência dos combustíveis fósseis e a adversidade climática.
---
### **Desafios da Energia Renovável**
Alcançar um futuro sustentável depende da adopção de fontes de energia renovável, mas estas enfrentam desafios únicos. Gerir o excesso de energia produzido durante períodos de baixa procura e lidar com as limitações da actual tecnologia de baterias são obstáculos significativos. Além disso, a transmissão de energia a longas distâncias permanece ineficiente, o que impede que recursos renováveis remotos alcancem mercados mais amplos.
Por exemplo, as linhas de corrente contínua de alta tensão (HVDC) perdem aproximadamente 3% de potência por cada 1.000 km, enquanto as linhas de corrente alternada de alta tensão (HVAC) perdem cerca de 7% por cada 1.000 km. Isto significa que, por cada quilómetro, as linhas HVDC perdem cerca de 0,003%, e as linhas HVAC perdem cerca de 0,007% (as linhas de alta tensão são projectadas para diminuir perdas, as perdas são ainda maiores na media tensão). Estas perdas, aliadas à dificuldade de transportar energia de parques renováveis remotos, sublinham a necessidade de soluções localizadas.
Por exemplo, em 2018, cerca de 6,5 milhões de MWh de produção de energia solar fotovoltaica foram descartados, ou "mandados fora", no Chile, na China, na Alemanha e nos Estados Unidos conjuntamente. É importante notar que, à medida que a capacidade de energia renovável continua a crescer rapidamente (com o aumento das adições de capacidade renovável global anual em quase 50%, para quase 510 gigawatts em 2023), a quantidade absoluta de energia desperdiçada é susceptível de aumentar, a menos que se façam melhorias significativas na infraestrutura da rede, no armazenamento de energia e na gestão da procura.
### **Monetizar o Excesso de Energia através da Mineração de Bitcoin**
Fontes de energia renovável, como a solar e a eólica, muitas vezes geram mais electricidade do que a rede necessita em determinados momentos, criando um excedente de energia que normalmente é desperdiçado. Este excesso permanece subutilizado porque:
- As soluções de armazenamento em grande escala são limitadas e dispendiosas ou mesmo inexistentes;
- A capacidade de transmissão muitas vezes não é suficiente para distribuir energia a longas distâncias;
- E a procura nem sempre coincide com os períodos de produção máxima de energia renovável.
A mineração de Bitcoin apresenta uma solução apelativa, ao actuar como um consumidor de energia flexível, capaz de ajustar rapidamente o seu consumo para se alinhar com a oferta. Operações de mineração localizadas perto de instalações de energia renovável — como centrais hidroeléctricas ou parques solares — podem absorver o excesso de energia que, de outra forma, seria desperdiçado, monetizando-o. Esta configuração não só reduz o desperdício de energia renovável, como também proporciona fontes de rendimento fiáveis para projectos renováveis, incentivando o investimento em infraestruturas verdes.
#### **Mineração de Bitcoin como Consumidor Flexível**
As operações de mineração de Bitcoin podem ajustar dinamicamente o seu consumo de energia, actuando como uma "carga flexível" na rede. As principais vantagens incluem:
- **Escalabilidade Rápida**: Os equipamentos de mineração podem aumentar ou diminuir o seu consumo de energia quase instantaneamente, respondendo às flutuações na disponibilidade de energia.
- **Independência Geográfica**: A mineração de Bitcoin pode ser realizada em qualquer local com ligação à internet, permitindo que os mineradores se situem perto das fontes renováveis, independentemente da infraestrutura da rede.
- **Capacidade Modular**: O equipamento de mineração é altamente escalável, permitindo que os produtores de energia desenhem sistemas modulares que se adaptem à capacidade energética disponível.
#### **Incentivos Económicos e Benefícios**
A utilização do excedente de energia para a mineração de Bitcoin permite que os produtores de energia renovável gerem receitas a partir de energia que, de outra forma, seria desperdiçada. Este impulso económico aumenta a rentabilidade dos projectos de energia renovável, tornando-os mais atractivos para os investidores. Os benefícios adicionais incluem:
- **Estabilização da Rede**: As operações de mineração ajudam a equilibrar a oferta e a procura na rede, contribuindo para a resiliência e estabilidade da mesma.
- **Redução do Desperdício**: Ao consumir electricidade excedente, a mineração de Bitcoin reduz significativamente a quantidade de energia renovável desperdiçada.
- **Aumento do Financiamento para Renováveis**: Os lucros provenientes da mineração de Bitcoin podem ser reinvestidos em novos projectos de energia renovável, soluções de armazenamento e infraestrutura de rede, criando um ciclo positivo de reforço para a energia verde.
#### **Aplicações no Mundo Real**
Vários exemplos ilustram como a mineração de Bitcoin monetiza eficazmente o excedente de energia:
- No Texas, os mineradores de Bitcoin aproveitam o excesso de energia eólica, apoiando a rede através de programas de resposta à procura que aumentam a fiabilidade da rede durante períodos de alta e baixa procura.
- No [Quebec](https://d-central.tech/the-untapped-potential-advocating-for-bitcoin-mining-as-a-key-to-quebecs-energy-future/), o excesso de energia hidroeléctrica é canalizado para operações de mineração de Bitcoin, o que ajuda a estabilizar a rede e a reduzir o desperdício de energia renovável.
- Um [estudo](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development) da Universidade de Cornell descobriu que projectos de energia renovável nos EUA poderiam gerar milhões de dólares ao minerar Bitcoin durante estágios pré-comerciais, demonstrando a viabilidade económica desta abordagem.
#### **Potencial Impacto na Transição para Energias Renováveis**
Ao monetizar o excedente de energia através da mineração de Bitcoin, esta abordagem acelera a transição para energias renováveis. Os benefícios incluem:
- **Viabilidade Económica para Renováveis**: A monetização da energia desperdiçada torna os projectos renováveis mais rentáveis e, portanto, mais atractivos para investidores.
- **Flexibilidade da Rede**: A mineração de Bitcoin fornece uma fonte de procura escalável e adaptável, ajudando os operadores de rede a gerir as flutuações de oferta.
- **Pegada de Carbono Reduzida**: Ao utilizar fontes renováveis, o impacto ambiental da mineração de Bitcoin diminui, alinhando-se com os objectivos de sustentabilidade.
- **Adopção Acelerada de Energias Renováveis**: A maior rentabilidade e a redução do desperdício incentivam um maior investimento, impulsionando a adopção de tecnologias de energia renovável.
Essencialmente, a mineração de Bitcoin oferece uma solução única para os desafios da produção intermitente de energia renovável, criando uma procura flexível e independente da localização para a electricidade excedente que, de outra forma, seria desperdiçada. À medida que mais projectos renováveis adoptam este modelo, a mineração de Bitcoin pode desempenhar um papel crucial na promoção de um panorama energético sustentável e descentralizado.
### **Fornecimento de Energia a Regiões Isoladas e Subdesenvolvidas**
Um dos impactos mais promissores da mineração de Bitcoin é a capacidade de levar electricidade a regiões remotas e subdesenvolvidas. Pequenas centrais hidroeléctricas e instalações solares são opções cada vez mais viáveis para comunidades isoladas que não têm acesso a redes tradicionais. Mineradores de Bitcoin, em busca de energia barata e excedente, podem apoiar e financiar estas instalações, reduzindo a lacuna energética e permitindo o acesso a energia limpa para estas comunidades.
Por exemplo, [aldeias](https://hackernoon.com/no-power-grid-this-african-village-mines-bitcoin-for-electricity) em África que anteriormente não tinham electricidade podem agora operar escolas, clínicas e empresas, graças a pequenos projectos de energia renovável apoiados pela mineração de Bitcoin. Este acesso catalisa o crescimento económico, criando um ciclo virtuoso onde a energia leva a investimentos, educação e melhor saúde — elevando comunidades inteiras para fora da pobreza.
### **Redução de Emissões através da Mitigação de Metano**
A mineração de Bitcoin também contribui para a redução das emissões de metano — um gás de efeito estufa com um potencial de aquecimento global 28 a 34 vezes superior ao do CO₂ num período de 100 anos. As emissões de aterros sanitários, resíduos agrícolas e poços de petróleo abandonados representam uma ameaça climática significativa, mas a mineração de Bitcoin oferece uma solução única ao converter este poluente em energia.
Quando o metano é queimado para gerar electricidade, é convertido em CO₂ e vapor de água, que, embora também sejam gases de efeito estufa, são muito menos potentes do que o metano. Na verdade, o metano é responsável por cerca de 25% do aquecimento global que experimentamos actualmente, apesar da sua concentração relativamente baixa na atmosfera. Ao capturar e utilizar o metano, as operações de mineração de Bitcoin transformam um dano ambiental numa fonte de energia produtiva, reduzindo as emissões globais de gases de efeito estufa e criando novas fontes de rendimento.
Por exemplo, nos EUA, o metano de poços de petróleo abandonados está a ser capturado para alimentar a mineração de Bitcoin, criando um sistema fechado que evita que o metano seja queimado ou liberado directamente na atmosfera. Esta abordagem não só mitiga as emissões, como também apoia o crescimento económico em regiões com recursos de metano não aproveitados.
### **Resiliência e Flexibilidade da Rede**
A integração de fontes renováveis, como a eólica e a solar, introduziu desafios para a estabilidade das redes eléctricas. Com as renováveis, os operadores de rede enfrentam flutuações de frequência mais frequentes e uma resposta inercial reduzida — as renováveis não fornecem a mesma resposta inercial que as centrais térmicas tradicionais, tornando a rede mais susceptível a mudanças rápidas.
A flexibilidade da mineração de Bitcoin pode desempenhar um papel fundamental na estabilização das redes eléctricas. Durante a tempestade de inverno Uri, no Texas, os mineradores de Bitcoin reduziram o seu consumo de energia para libertar capacidade para serviços essenciais, mostrando o papel da mineração de Bitcoin como uma carga flexível e reactiva de energia.
Ao ajustar o consumo de energia com base na disponibilidade de oferta, os mineradores de Bitcoin podem ajudar a equilibrar as redes com elevada penetração de renováveis. Esta sinergia com energias renováveis e nucleares fornece uma solução robusta para a gestão da procura energética, especialmente à medida que a rede transita para fontes de baixo carbono.
### **Impacto Ambiental de Longo Prazo**
A mineração de Bitcoin tem o potencial de revolucionar a produção e o consumo de energia. Ao integrar energias renováveis, aproveitar o metano e oferecer gestão flexível da carga, o Bitcoin pode desempenhar um papel fundamental num futuro energético sustentável e descentralizado. Inovação política, responsabilidade industrial e colaboração intersectorial são essenciais para concretizar o potencial do Bitcoin na transição verde.
Diante dos desafios ambientais actuais, a mineração de Bitcoin oferece mais do que inovação financeira. Representa um poderoso aliado na construção de um futuro sustentável e equitativo — onde os objectivos digitais e ambientais alinham-se para criar uma economia global mais limpa e resiliente.
#Bitcoin #mining #greenEnergy #renewables
---
_Photo by [Anders J]("https://unsplash.com/@aj5photos?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash") on [Unsplash]("https://unsplash.com/photos/white-and-blue-solar-panels-hxUcl0nUsIY?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_
-

@ 20986fb8:cdac21b3
2024-10-30 12:30:09
**Hey Nostriches! **
Thrilled to launch the latest YakiHonne update—Simpler, Easier, Faster! After a lot of hard work, we bring you a highly optimized, user-friendly decentralized media experience on both web and mobile. This version focuses on two main aspects:
**1. Complete Redesign:**
Our UI/UX now puts simplicity first, minimizing technicalities for creators and social users alike. Here’s what’s new:
• Onboarding: Easily create a non-custodial wallet with Npub & Nsec, experience zapping (Lightning payments), or browse as a guest.
• Home & Discover: “Discover” is designed for creators, focusing on rich formats like long-form content, videos, and curated works. “Home” offers a social feed with short notes and curated contents, making it quick and easy for creators to share their work.
• Wallet: Simple setup with easy creation, direct YakiHonne node linking, and multi-wallet support.
• Dashboard: Manage all published and drafted content, check stats, and pick up right where you left off—all in one place.
• Notifications: Reactions, Reposts, Mentions, Zaps, Comments, and Follows now appear in clear, categorized cards.
• Settings: Completely revamped for simplicity, now including profile customization, appearance, relay settings, and wallet management.
**2. Enhanced Performance:**
Our re-engineered core now supports the outbox model with extensive functionality. Furthermore, Thanks to @PabloF7z we now have seamless data fetching, caching, and full support of the NDK implementation.
Hope you enjoy the new decentralized media experience! 🌐✨Try it out here:
**•Web**: yakihonne.com
**•App Store (iOS)**: https://apps.apple.com/us/app/yakihonne/id6472556189
**•Google Play (Android)**: https://play.google.com/store/apps/details?id=com.yakihonne.yakihonne&hl=en
Thank you for your incredible support on this decentralized media journey!
https://v.nostr.build/Uu1uXf8P5D9KkBw6.mp4
-

@ 4c48cf05:07f52b80
2024-10-30 01:03:42
> I believe that five years from now, access to artificial intelligence will be akin to what access to the Internet represents today. It will be the greatest differentiator between the haves and have nots. Unequal access to artificial intelligence will exacerbate societal inequalities and limit opportunities for those without access to it.
Back in April, the AI Index Steering Committee at the Institute for Human-Centered AI from Stanford University released [The AI Index 2024 Annual Report](https://aiindex.stanford.edu/report/).
Out of the extensive report (502 pages), I chose to focus on the chapter dedicated to Public Opinion. People involved with AI live in a bubble. We all know and understand AI and therefore assume that everyone else does. But, is that really the case once you step out of your regular circles in Seattle or Silicon Valley and hit Main Street?
# Two thirds of global respondents have a good understanding of what AI is
The exact number is 67%. My gut feeling is that this number is way too high to be realistic. At the same time, 63% of respondents are aware of ChatGPT so maybe people are confounding AI with ChatGPT?
If so, there is so much more that they won't see coming.
This number is important because you need to see every other questions and response of the survey through the lens of a respondent who believes to have a good understanding of what AI is.
# A majority are nervous about AI products and services
52% of global respondents are nervous about products and services that use AI. Leading the pack are Australians at 69% and the least worried are Japanise at 23%. U.S.A. is up there at the top at 63%.
Japan is truly an outlier, with most countries moving between 40% and 60%.
# Personal data is the clear victim
Exaclty half of the respondents believe that AI companies will protect their personal data. And the other half believes they won't.
# Expected benefits
Again a majority of people (57%) think that it will change how they do their jobs. As for impact on your life, top hitters are getting things done faster (54%) and more entertainment options (51%).
The last one is a head scratcher for me. Are people looking forward to AI generated movies?

# Concerns
Remember the 57% that thought that AI will change how they do their jobs? Well, it looks like 37% of them expect to lose it. Whether or not this is what will happen, that is a very high number of people who have a direct incentive to oppose AI.
Other key concerns include:
- Misuse for nefarious purposes: 49%
- Violation of citizens' privacy: 45%
# Conclusion
This is the first time I come across this report and I wil make sure to follow future annual reports to see how these trends evolve.
**Overall, people are worried about AI. There are many things that could go wrong and people perceive that both jobs and privacy are on the line.**
---
Full citation: *Nestor Maslej, Loredana Fattorini, Raymond Perrault, Vanessa Parli, Anka Reuel, Erik Brynjolfsson, John Etchemendy, Katrina Ligett, Terah Lyons, James Manyika, Juan Carlos Niebles, Yoav Shoham, Russell Wald, and Jack Clark, “The AI Index 2024 Annual Report,” AI Index Steering Committee, Institute for Human-Centered AI, Stanford University, Stanford, CA, April 2024.*
The AI Index 2024 Annual Report by Stanford University is licensed under [Attribution-NoDerivatives 4.0 International](https://creativecommons.org/licenses/by-nd/4.0/?ref=chooser-v1).
-

@ f462d21e:1390b6b1
2024-10-29 20:24:39
eyJfaWQiOiJiMDYzYjQxMi04MGNmLTQxOTUtOTFhOS03MTM0MzExNDI4ZGIiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6IkNBU0hfQllfTUFJTCIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjo0LCJtYXJrZXRQcmljZSI6MTY0LjE4LCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwicGF5bWVudE1ldGhvZERldGFpbCI6ImZhc3QgcmVwbHkiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yOVQyMDoyNDozOS44NzRaIn0=
-

@ 3f770d65:7a745b24
2024-10-29 17:38:20
**Amber**
[Amber](https://github.com/greenart7c3/Amber) is a Nostr event signer for Android that allows users to securely segregate their private key (nsec) within a single, dedicated application. Designed to function as a NIP-46 signing device, Amber ensures your smartphone can sign events without needing external servers or additional hardware, keeping your private key exposure to an absolute minimum. This approach aligns with the security rationale of NIP-46, which states that each additional system handling private keys increases potential vulnerability. With Amber, no longer do users need to enter their private key into various Nostr applications.
<img src="https://cdn.satellite.earth/b42b649a16b8f51b48f482e304135ad325ec89386b5614433334431985d4d60d.jpg">
Amber is supported by a growing list of apps, including [Amethyst](https://www.amethyst.social/), [0xChat](https://0xchat.com/#/), [Voyage](https://github.com/dluvian/voyage), [Fountain](https://fountain.fm/), and [Pokey](https://github.com/KoalaSat/pokey), as well as any web application that supports NIP-46 NSEC bunkers, such as [Nostr Nests](https://nostrnests.com), [Coracle](https://coracle.social), [Nostrudel](https://nostrudel.ninja), and more. With expanding support, Amber provides an easy solution for secure Nostr key management across numerous platforms.
<img src="https://cdn.satellite.earth/5b5d4fb9925fabb0005eafa291c47c33778840438438679dfad5662a00644c90.jpg">
Amber supports both native and web-based Nostr applications, aiming to eliminate the need for browser extensions or web servers. Key features include offline signing, multiple account support, and NIP-46 compatibility, and includes a simple UI for granular permissions management. Amber is designed to support signing events in the background, enhancing flexibility when you select the "remember my choice" option, eliminating the need to constantly be signing events for applications that you trust. You can download the app from it's [GitHub](https://github.com/greenart7c3/Amber) page, via [Obtainium ](https://github.com/ImranR98/Obtainium)or Zap.store.
To log in with Amber, simply tap the "Login with Amber" button or icon in a supported application, or you can paste the NSEC bunker connection string directly into the login box. For example, use a connection string like this: bunker://npub1tj2dmc4udvgafxxxxxxxrtgne8j8l6rgrnaykzc8sys9mzfcz@relay.nsecbunker.com.
<img src="https://cdn.satellite.earth/ca2156bfa084ee16dceea0739e671dd65c5f8d92d0688e6e59cc97faac199c3b.jpg">
---
**Citrine**
[Citrine](https://github.com/greenart7c3/Citrine) is a Nostr relay built specifically for Android, allowing Nostr clients on Android devices to seamlessly send and receive events through a relay running directly on their smartphone. This mobile relay setup offers Nostr users enhanced flexibility, enabling them to manage, share, and back up all their Nostr data locally on their device. Citrine’s design supports independence and data security by keeping data accessible and under user control.
<img src="https://cdn.satellite.earth/46bbc10ca2efb3ca430fcb07ec3fe6629efd7e065ac9740d6079e62296e39273.jpg">
With features tailored to give users greater command over their data, Citrine allows easy export and import of the database, restoration of contact lists in case of client malfunctions, and detailed relay management options like port configuration, custom icons, user management, and on-demand relay start/stop. Users can even activate TOR access, letting others connect securely to their Nostr relay directly on their phone. Future updates will include automatic broadcasting when the device reconnects to the internet, along with content resolver support to expand its functionality.
Once you have your Citrine relay fully configured, simply add it to the Private and Local relay sections in Amethyst's relay configuration.
<img src="https://cdn.satellite.earth/6ea01b68009b291770d5b11314ccb3d7ba05fe25cb783e6e1ea977bb21d55c09.jpg">
---
**Pokey**
[Pokey](https://github.com/KoalaSat/pokey) for Android is a brand new, real-time notification tool for Nostr. Pokey allows users to receive live updates for their Nostr events and enabling other apps to access and interact with them. Designed for seamless integration within a user's Nostr relays, Pokey lets users stay informed of activity as it happens, with speed and the flexibility to manage which events trigger notifications on their mobile device.
<img src="https://cdn.satellite.earth/62ec76cc36254176e63f97f646a33e2c7abd32e14226351fa0dd8684177b50a2.jpg">
Pokey currently supports connections with Amber, offering granular notification settings so users can tailor alerts to their preferences. Planned features include broadcasting events to other apps, authenticating to relays, built-in Tor support, multi-account handling, and InBox relay management. These upcoming additions aim to make Pokey a fantastic tool for Nostr notifications across the ecosystem.
---
**Zap.store**
[Zap.store](https://github.com/zapstore/zapstore/) is a permissionless app store powered by Nostr and your trusted social graph. Built to offer a decentralized approach to app recommendations, zap.store enables you to check if friends like Alice follow, endorse, or verify an app’s SHA256 hash. This trust-based, social proof model brings app discovery closer to real-world recommendations from friends and family, bypassing centralized app curation. Unlike conventional app stores and other third party app store solutions like Obtainium, zap.store empowers users to see which apps their contacts actively interact with, providing a higher level of confidence and transparency.
<img src="https://cdn.satellite.earth/fd162229a404b317306916ae9f320a7280682431e933795f708d480e15affa23.jpg">
Currently available on Android, zap.store aims to expand to desktop, PWAs, and other platforms soon. You can get started by installing [Zap.store](https://github.com/zapstore/zapstore/) on your favorite Android device, and install all of the applications mentioned above.
---
Android's openness goes hand in hand with Nostr's openness. Enjoy exploring both expanding ecosystems.
-

@ f462d21e:1390b6b1
2024-10-29 17:01:09
eyJfaWQiOiJmOWQ2ZmEyOS1iNTI5LTQyMzktOTMyNS0xMzIzMjE0MzcxZWYiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwibWFya2V0UHJpY2UiOjE2NS4yOSwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjowLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yOVQxNzowMTowOS44NzRaIn0=
-

@ 4ba8e86d:89d32de4
2024-10-29 12:30:05
## Tutorial feito por Grom Mestre⚡
Poste original Abaixo.
Part 1: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/229987/tutorial-entendendo-e-usando-a-rede-i2p-introdu%C3%A7
Part 2: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/230035/tutorial-instalando-e-configurando-o-roteador-i2p?show=230035#q230035
Part 3: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/230113/tutorial-conectando-se-ao-xmpp-pela-i2p?show=230113#q230113
Boa tarde, camaradas do meu coeur!
Depois de muito tempo, e com o retorno da minha serotonina aos níveis basais, estou dando início a essa nova série de tutoriais. Espero que tirem muito proveito das informações passadas aqui para amplicarem o seu conhecimento da deepweb.
Esta postagem trará antes algumas considerações iniciais que podem ser úteis para quem possui pouco ou nenhum contato prévio com outras tecnologias ou tenha um entendimento torto a respeito da deepweb. Aconselho a estes que deem um boa lida antes de partirem para os tópicos do tutorial, mas saibam que ele não é um pré requisito para ele.
Dito isso, vamos prosseguir.
TÓPICOS:
Introdução
Instalando e configurando o roteador e o navegador
Conectando-se a serviços na I2P
Configurações avançadas
## 1. Introdução
### 1.1 Definindo a DeepWeb.
Muitos devem imaginar erroneamente que a deepweb se restrinja apenas à rede onion, mais precisamente aos seus hidden services, já que o Tor possui como uma das suas funções primárias proteger e burlar restrições governamentais e proteger o seus usuários através de métodos sofisticados de roteamento de pacotes e criptografia. Entretanto, ela é mais ampla do que se imagina dependendo da forma como a classificamos.
Os ditos "profissionais" usam uma definição extremamente vaga e imprecisa do que seria a deepweb e a sua verdadeira abrangência. Para isso, criei uma definição um pouco melhor para ela: redes comunitárias, sobrepostas, anônimas e criptografadas.
Vamos aos pontos individualmente:
> São Comunitárias, pois os pontos de roteamento de pacotes na rede (relays ou routers) muitas vezes são mantidos de forma voluntária por usuários comuns. Não é necessário nenhuma infraestrutura sofisticada para ser um contribuinte na rede, basta ter um computador com acesso à internet e conhecimentos básicos para fazer a configuração.
> São sobrepostas porque não estão acima ou abaixo da rede tradicional (diferente do que muitos imaginam). Os pacotes na DW trafegam entre os dados da surface e não em meios distintos (algo que não faz o menor sentido). Sabe aquele papo de camadas da DW ou aquela abobrinha da Mariana's Web? Então, tudo um monte de bosta derivado de Youtubers sensacionalistas iletrados em informática. Elitismo da minha parte? Quem sabe...
> São anônimas porque não é simples determinar a origem e o destino dos pacotes entre nodes intermediários dado a natureza do roteamento. Em geral, aos menos para a rede onion, há pelo menos 3 relays entre você e o servidor, sendo que esse número duplica para hidden services (3 seus e 3 do serviço). A imagem abaixo ilustra bemocoteamento dos pacotes na onio.
https://image.nostr.build/aea96f41d356157512f26b479ea8db5bce8693dd642f2bce0258d8e4b0dac053.jpg
> Por fim, são criptografadas porque as conexões são fortemente protegidas por algoritmos sofisticados de criptografia. Além de não sabermos a origem dos dados, sequer podemos saber com facilidade o conteúdo dessas mensagens mesmo que os protocolos das camadas superiores (HTTP, HTTPS, FTP) sejam inseguros, dado que a criptografia da própria rede já as protege. Por isso é tão comum que sites da DW não usem HTTPS, pois as autoridades de certificados não os assinam para domínios da onion e certificados autoassinados vão disparar avisos no navegador.
A imagem abaixo ilustra bem como é o roteamento onion usado pelo Tor. Perceba que o contéudo da mensagem está enrolado em 3 camadas de criptografia (como a de uma cebola), de modo que para revelar o contéudo original seria preciso quebrar, no pior dos casos, 3 camadas. Como mencionado antes, o método usado para isso é a criptografia assimétrica, muito similar ao PGP, porém com a sua própria implementação.
https://image.nostr.build/7bfaaf29211c11b82049ef8425abb67738d085c41558e9339ec13cf49ea5b548.jpg
Observação: Por mais que dentro da rede o encapsulamento proteja as mensagens internamente, entenda muito bem que isso não se aplica a sites da surface acessados pela onion. Ao desempacotar a última camada, a mensagem original é completamente exposta no exit node. Se ela não estiver protegida por uma camada adicional como TLS, seus pacotes estarão completamente expostos, algo que representa um sério risco de segurança.
As redes que caem em ao menos três dessas definições (anonimato, sobreposição e criptografia) podem ser classificadas como deepwebs. Podemos citar:
• Lokinet
• Zeronet
• Freenet
• I2P
• Tor
• Gnunet
Porém, há alguns casos interessantes que não caem diretamente nessa regra .
A Yggdrasil ( https://yggdrasil-network.github.io/ ), uma rede de topologia mesh com foco em escalabilidade e eficiência de roteamento, possui três dessas características: comunitária, sobreposta e segura. Entretanto, os nodes não são anônimos e muitas vezes podem estar desprotegidos, já que se conectar à Yggdrasil é que equivalente a ligar o seu computador diretamente na rede sem a presença de um NAT/CGNAT, correndo o risco de expor portas de serviços da sua máquina caso elas não estejam protegidas por um firewall. A Yggdrasil na prática é exposta como um dispositivo de camada 3 (tipo um VPN), mas diferente de um, apenas endereços IPv6 dentro de uma faixa bem específica de IP são roteados por ela, o que permite que ela coexista com outros dispositivos sem haver conflitos de roteamento.
Há quem argumente que a Yggdrasil é uma deepweb dado a sua sobreposição em relação à surface; outros podem argumentar que dado a falta de anonimato ela não se enquadraria nessa categoria. Independentemente disso é uma tecnologia muito interessante com ampla gama de aplicações, como encapsular tráfego de outras redes, como a I2P, e melhorar a eficiência de roteamento.
Por fim, vamos desmitificar alguns mitos da DeepWeb muito difundidos.
Não existem camadas da DW. Os pacotes da DW são sobrepostos e navegam juntos aos pacotes da surface.
DeepWeb e DarkWeb não são coisas diferentes. São termos genéricos para a mesma coisa.
DarkWeb não é o seu provedor de e-mail ou serviço de banco. Se eles não se enquadram nas categorias de um deepweb, então estão na surface.
Você não é irrastreável na DW. Adversários motivados podem foder com você com facilidade (leia a respeito de ataques de Timing, correlação e fingerprinting).
Mesmo que não seja possível ver o conteúdo de uma mensagem pela deepweb, é possível ao menos saber que você a acessou. ISPs podem ver esse tipo de tráfego como suspeito.
Você não é um hacker só porque instalou o TorBrowser, mas pode ser considerado um se expor o IP de um hidden service.
## Instalando e configurando o roteador I2P
Segue agora a seção 2 do tutorial do I2P. Mas antes apenas queria falar um pouco do projeto I2P. Apesar do foco do tutorial não ser para tratar da sua história, gostaria ao menos de fazer uma breve introdução sobre ela.
O projeto I2P (Invisible Internet Protocol) é uma rede P2P descentalizada, anônima e segura para estabelecer a comunicação entre os usuários e serviços. Na I2P é possível usar serviços como mensageiros IRC, XMPP, web services, e-mail e até mesmo torrents. A I2P nasceu de um fork da Freenet no ano de 2003, porém possui diferenças drásticas em relação a ela.
Há similaridades entre a I2P e o Tor, porém vale destacar algumas de suas vantagens. Sendo elas:
• Garlic routing ( https://geti2p.net/en/docs/how/garlic-routing )
• Modelo P2P
• Todos os participantes da rede contribuem para ela
• Fechado na rede - não é possível acessar a surface através da I2P
• Otimizado para hidden services
Apesar disso, vale lembrar que o projeto é pequeno, desenvolvido por menos voluntários se comparado ao Tor e possui menos movimentação e financiamento para o seu desenvolvimento. Além disso, o Tor é um projeto muito mais maduro e bem documentado, algo que atrai mais usuários e desenvolvedores e torna a tarefa de encontrar e corrigir bugs mais fácil de ser realizada.
Esses são pontos importantes que devemos levar em conta ao escolher a tecnologia para as nossas necessidades. Nem sempre há tecnologias ruins, as vezes apenas as empregamos as ferramentas erradas na resolução de certos problemas.
Referências:
• https://geti2p.net/en/comparison/tor
• https://geti2p.net/en/docs/how/garlic-routing
• https://geti2p.net/en/about/intro
• https://i2pd.readthedocs.io/en/latest/
### 2. Instalando e configurando o roteador
Antes da criação do I2PBrowserBundle ( https://github.com/PurpleI2P/i2pdbrowser/releases/tag/1.3.3 ) , a única forma de se conectar à I2P era pela configuração manual de proxy no navegador. Muita gente ou não sabe ou tem MUUUUUITA preguiça de fazer isso e ficam resistentes de entrar na I2P dada essa restrição.
Como eu quero ser um bom tutor eu farei do jeito mais "difícil", pois tanto eu desejo que vocês aprendam as nuances do processo como eu sei que vocês são inteligentes o suficiente para fazer isso.
### 2.1 Instalação do router
Atualmente nós temos duas implementações do I2P: Uma em Java e outra em C++ (i2pd). Usaremos nesse tutorial a versão em C++ dado o seu baixo uso de recursos e facilidade de instalação.
O I2Pd está disponível para Windows, Linux, MacOS e Android e possui binários pré-compilados nas releases ( https://github.com/PurpleI2P/i2pd/releases/tag/2.50.2 ) do projeto no Github. Usuários de Linux podem instalá-lo através do respectivo gerenciador de pacotes da sua distribuição, porém algumas distros não oferecem o pacote diretamente nos reposítórios oficiais, necessitando do uso de PPAs (Ubuntu), COPR (Fedora/RHEL) e afins. Vocês podem conferir as instruções oficiais para cada sistema nessa página ( https://i2pd.readthedocs.io/en/latest/user-guide/install/ ).
Apesar desse tutorial ser voltado a usuários de desktop, o I2Pd também está disponível na loja do F-droid. Infelizmente poucos navegadores em Android permitem a configuração de proxies, porém na seção de Serviços na I2P eu tratarei brevemente de como se conectar a servidores de XMPP usando o ConversationI2P.
Para usuários de Windows, segue abaixo os binários para instalação.
• Versão 32bits ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_win32_mingw.zip )
• Versão 64bits ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_win64_mingw.zip )
• Versão para Windows XP (pois é, kk) ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_winxp_mingw.zip )
A instalação é simples e direta. Após ela apenas abram o I2Pd para que o router inicie a operação de busca e conexão com os peers. Para usuários de Linux, vocês precisam ativar o serviços através do comando 'sudo systemctl start i2pd'. Se vocês desejam que o I2Pd inicie junto com o sistema usem o comando 'sudo systemctl enable --now i2pd'.
Se tudo estiver funcionando corretamente, vocês serão capazes de abrir o webconsole do I2Pd no navegador através do endereço: 127.0.0.1:7070.
https://image.nostr.build/ab205ae1071a2b705279e5ce2d6e912d8d11cc7d6dd0dc8a26b76724a27bd94b.jpg
https://image.nostr.build/fa17e14600737ccfc92a415cec2fbfba226b950b2b97af7475927ae65abdbe11.jpg
### 2.2 Instalação e configuração do navegador
Apesar de qualquer navegador ser capaz de usar a I2P não é recomendado que usem qualquer um, especialmente o navegador que você usam no seu dia-a-dia. Recomendo que usem um navegador próprio para usar na I2P ou isolem suas atividades em um perfil separado.
Em navegadores baseado no Firefox isso é relativamente simples, bastando adicionar a opção '--profile' e o caminho do perfil que vocês desejam usar. Nesse tutorial eu vou mostrar como criar um perfil novo no Librewolf e configurar no lançador para iniciar o perfil e abrir em uma janela anônima. Essas instruções são análogas para todos os sistemas, excetuando aquelas configurações mais exóticas.
### 2.2.1 Escolhendo o navegador
Como citado, usarei o Librewolf como exemplo. Vocês podem baixar o instalador direto do site ou usar o gerenciador de pacotes do seu sistema no caso de Linux. Como é uma tarefa trivial eu não vou detalhar esse processo, pois todas as instruções estão em detalhes no site do navegador ( https://librewolf.net/installation/ )
### 2.2.2 Criando um perfil e configurando o lançador
Abram o navegador e digitem 'about:profiles' na barra de endereço. Criem um novo perfil clicando em 'Create New Profile'
https://image.nostr.build/fa17e14600737ccfc92a415cec2fbfba226b950b2b97af7475927ae65abdbe11.jpg
Coloquem um nome no seu perfil e cliquem em Finalizar
https://image.nostr.build/62059e375000940f11b27ae77b9ec011f9baadbb5a84afc910d41841ce73e82d.jpg
Perfis novos recém criados são iniciados por padrão. Se você deseja usar outro perfil por padrão deve mudar isso na seção 'about:profiles' do navegador.
Agora vamos configurar o lançador do LibreWolf para iniciar o perfil do i2p e em uma janela anônima. Usarei o XFCE como referência para essa tarefa, mas saibam que o processo é análogo em sistemas como Windows ou DEs como KDE. Se quiserem também podem lançar via terminal através do comando 'librewolf --profile caminho_do_perfil --private-window'.
Cliquem com o botão direito no ícone do Librewolf e abram as propriedades do atalho.
Na guia lançador, no campo Comando, adicionem no final a opção '--private-window' e a opção '--profile caminho_do_perfil'. O caminho do perfil é aquele mostrado na seção 'about:profiles' do Librewolf.
https://image.nostr.build/a7d6515d7825cb3bdcb681ecf71a97318dccba81eea7cc87fc5377ecc06065ee.jpg
2.2.3 Configurando o proxy
Com o lançador configurado, abra o navegador nesse perfil. Vamos configurar o proxy para se conectar ao I2P agora.
Abra as configurações digitando 'about:preferences' na barra de endereço. Na seção 'Geral' abra as configurações de rede (Network Settings)
https://image.nostr.build/f37157bebf15ada616914f403e756cf9fcee4c9aaaa353196c9cc754ca4d7bc5.jpg
Configure o seu proxy como na figura abaixo.
https://image.nostr.build/41ebd05255a8129d21011518d400689308d9c0320408967003bf296771e0b96f.jpg
Fecha as configurações. Se o seu proxy foi configurado corretamente tente abrir algum desses eepsites.
• http://identiguy.i2p
• http://notbob.i2p
• http://reg.i2p
Se tudo ocorreu como conforme, a página será carregada.
https://image.nostr.build/ce29ae44743f06cfed591f082208c9612c59b3429ab46d90db48131b3bc3e99d.jpg
OBSERVAÇÃO: A busca pelos peers é um pouco demorada, levando de 2 a 5 minutos para que um número mínimo necessário de peers sejam encontrados para estabelecer uma conexão estável. Você pode ver a lista de inbound e outbound tunnels na seção Tunnels do WebConsole (localhost:7070)
https://image.nostr.build/285a0d765eaf5f33409f975cd720d0efa68ecc40a9da20bfd9cde0cd1f59a7b6.jpg
IMPORTANTE: Apesar do Librewolf possuir defaults seguros, eu recomendo que vocês instalem as seguintes extensões para aumentar ainda mais a sua proteção.
• noScript
• JShelter
Lembrem-se que vocês precisam desativar o proxy para acessar a clearnet. Depois disso reativem-no nas configurações.
Outro detalhe: Se vocês tentarem digitar um endereço .i2p na barra de endereços do navegador sem especificar o protocolo (http), ao invés do Librewolf ir ao endereço ele vai realizar uma pesquisa. Para corrigir esse problema, vocês precisam adicionar a seguinte configuração do tipo boolean em 'about:config' como mostrado na imagem.
https://image.nostr.build/4518ab817b131f7efe542b2d919b926099dce29a7b59bdd3c788caf53dbd071e.jpg
Reiniciem o navegador e testem. Se tudo deu certo vocês não precisam especificar o protocolo ao digitar um endereço .i2p, bastando apenas digitar o endereço simplificado.
Por fim, terminamos essa parte do tutorial. Na próximo parte trataremos de como podemos nos conectar a serviços hospedados na I2P como XMPP
## [TUTORIAL] Conectando-se ao XMPP pela I2P
Essa é a terceira parte da série de tutoriais. Agora vamos tratar de algumas operações na rede, sendo uma delas conectando-se a um servidor de XMPP na I2P.
Não se esqueça de ligar o router e manter ele ligado por alguns minutos antes de iniciar essas operações. O router demora um pouco para encontrar os peers e estabelecer uma conexão estável.
### 3.1 Escolhendo o cliente XMPP
Existem diversos clientes XMPP capazes de se conectar usando um proxy. Um dos melhores é o Gajim, um cliente escrito em Python com diversas funcionalidades como criptografia OMEMO e PGP, workspaces separados, extensibilidade via plugins e uma interface bonita e organizada.
Assim como ocorreu com o router, o Gajim está disponível por padrão na maioria das distros Linux. Use o seu gerenciador de pacotes para instala-lo. Em Windows você pode baixar o Gajim através desse link ( https://gajim.org/download/ )
### 3.2 Criando uma conta
Vamos primeiro criar uma conta no servidor. No nosso exemplo usarei o servidor oficial do projeto i2pd, o xmpp.ilita.i2p. Há diversos outros servidores XMPP no diretório de links notbob.i2p caso queiram explorar mais.
Para criar uma conta, siga os passos abaixo:
Abra o Gajim. Na barra de tarefas vá em Contas -> Adicionar Conta. Na nova janela que aparecer, clique em Adicionar Conta
https://image.nostr.build/01413e7c6d00c238420e3b0c769dd8d7f7d6522754d2135d3e98a22944f79a27.jpg
https://image.nostr.build/9f015861f33990871d96f03d5ec78036a65e3ad9f8ff6a38da18c5b27d31f6d5.jpg
Na janela de adicionar contas, clique diretamente em Inscrever-se. Não precisa colocar as suas credencias como mostra a imagem (falha minha, ksksk)
https://nostrcheck.me/media/c8411a22946e97467e0ee197ef7a0205ba05f2c67bde092041481ccc2cbbc66d/81938c8d278ce0562c2240341e203f3b70f51ee2db06ceb453f8a178df37fa84.webp
Digite o nome do servidor no campo abaixo. Não esqueça de marcar a opção 'Configurações Avançadas' antes de clicar em Inscrever-se
https://image.nostr.build/5ee4305a6a23e5c064446b0ce7a4cbc7e790c1ba237bd2495d0237b86a4df07f.jpg
Vamos adicionar um novo proxy para essa conta. Para isso clique no botão 'Gerenciar proxies', ao lado do campo Proxy nas Configurações Avançadas
https://image.nostr.build/daceb5436def55401d3974ce48d85771e5ebcec4e3f90eb1001df4609112ec12.jpg
Adicione um novo proxy clicando no sinal de '+' abaixo da lista de proxies. Preencha os campos de acordo com a imagem abaixo e em seguida feche a janela.
https://image.nostr.build/140b34c4e46e9295c073311d483d206201d9339a75f613fe4e829c14f3257bfe.jpg
https://image.nostr.build/d365a63d81a14d763bffceb50b30eb53d81959623f8fe812175358a41b1fba53.jpg
No campo de Proxy, selecione o proxy I2P. Preencha o restante dos campos de acordo com a imagem abaixo. Em seguida clique em 'Inscrever-se'.
https://image.nostr.build/d06c11d9c6d19728bf5a58af2dd3e14d8ca0021456da09792a345ac0bfc90ad0.jpg
Nesse momento uma mensagem pode aparecer pedindo para abrir uma exceção para o certificado TLS. Isso acontece porque trata-se de um certificado autoassinado que não foi validado por uma autoridade oficial. Apenas abra a exceção e prossiga (não há imagem para isso porque eu já abri essa exceção no meu cliente).
Uma nova janela vai aparecer solicitando-lhe para inserir as suas credenciais. Tome cuidado aqui, pois não é para inserir o nome completo com o domínio, apenas o seu nome de usuário (ex: descartavel).
https://image.nostr.build/dde2a6736bd00080fbeeb8076754e226971a412710b370d5559f7f4d5414f8b3.jpg
Se tudo der certo, uma nova janela vai aparecer confirmando a sua inscrição. Coloque um nome e uma cor para a sua conta e clique em Conectar para concluir o processo.
https://image.nostr.build/74934d3f1f3f4232eacee8e78e707936227f816c50ac6b52da5c81ec17557e69.jpg
Para finalizar, nos detalhes da sua conta, modifique as suas configurações de privacidade para diminuir o fingerprint. Na seção de 'Privacidade', desligue as seguintes opções:
• Tempo ocioso
• Hora de Sistema Local
• Sistema Operacional
• Reprodução de Mídia
https://image.nostr.build/d2ed5852a104c770b50c7b053d518d8af0b6289ced6b3ad4187492208c7ca649.jpg
### 3.3 Procurando por salas de bate-papo públicas
Após criar a sua nova conta, vamos descobrir alguns serviços que o servidor oferece. Para isso, vá para Contas -> Descobrir serviços
https://image.nostr.build/54928d1dd0e48365858b24c72097a9fabf677794e13f329fc0568211eefbe559.jpg
Na seção 'Bate-papo em Grupo', selecione Chatrooms e clique em 'Navegar'. Ao fazer isso uma lista de chatroom públicos presentes no servidor vai aparecer. Fique a vontade para explorar, porém saiba que alguns servidores são moderados e não te permitem mandar mensagens sem sua conta ser aprovada pelo moderador (familiar?).
https://image.nostr.build/1936bef51d58a1f6cfdf8bf8d84bfa64adc2a09b9c0fb1623b93a327f0b8cdd8.jpg
https://image.nostr.build/89e8013b1cea1df0f80f6833bd6771c33101f404b0099b2d7330a5e57607baff.jpg
### 3.4 Adicionando contatos
Para adicionar contatos à sua lista, clique no símbolo de '+' ao lado do campo de pesquisa e selecione 'Add Contact'.
https://image.nostr.build/d3cadea27591355f674fba93765c3815282d112b2e80a592bb77a442c13dd4f4.jpg
Coloque o endereço completo da conta que você deseja adicionar. Usarei a minha conta oficial nesse exemplo. Você tem a opção de anexar uma mensagem qualquer antes de enviar o convite. Clique em 'Adicionar Contato' para prosseguir.
https://image.nostr.build/ff95b7aec2377c58d4253c5b7b3aabf141a92dd5f3e97f6e1f01ecb32a215d38.jpg
https://image.nostr.build/6562e680e28c321ebbd009b5ade513f8a279aea33bc16aa9fb251f3507eb04af.jpg
Se tudo ocorrer normalmente, o novo contato vai aparecer na sua lista. Dê dois-cliques na conta para abrir o chat. Não se esqueça de ativar a criptografia OMEMO antes de enviar qualquer mensagem. Agora você está pronto para conversar de forma segura :)
https://image.nostr.build/ef7f783a311ad0f68a5408137f75dc2bc6c38f6e9656dc0d68d3267f5012f658.jpg
E com isso terminamos a terceira parte da série de tutoriais.
## [TUTORIAL] Criando e conectando-se a um servidor XMPP na I2P e clearnet.
Como configurar o seu próprio servidor XMPP. https://youtube.com/watch?v=Ot_EmQ8xdJwy
Criando contas e conectando clientes Pidgin http://i2pd.readthedocs.io/en/latest/tutorials/xmpp/#creating-accounts-and-connecting-clients
BONUS: Conectando-se facilmente à I2P.
https://youtube.com/watch?v=wGIh5tQcw68
-

@ fd208ee8:0fd927c1
2024-10-29 08:52:42
## Yesterday was also a day
I'm still quite bullish about using Nostr to publish, and generally for OtherStuff, but I was feeling a bit pessimistic about the microblogging (kind 01) feeds on Nostr, yesterday. And, rightly so. Mine has been grinding slowly to a halt, and not for lack of effort, on my part. I regularly hear reports, from other npubs, that they sense the same phenomenon.
Most of the people I have whitelisted on the wss://theforest.nostr1.com relay (currently 302, in number) are beginning to give up on Kind 01 clients, except for occasionally making an announcement, and are increasingly moving their chatting off-Nostr. (I'm still privy to those conversations, but most of you no longer are.)
So, my feed has been getting quieter and quieter. Even adding new people doesn't help much, as they don't tend to stick around, for long, so it's a Sisyphean task.

Some others are still bothering to show up, regularly, but they increasingly see it as a chore, or something they do to "keep up appearances". Add me to this group of wearied, diligent noters, holding down the microblogging feeds, with our exhausting attempt at #KeepingNostrWeird, while the influencers surround the gates and the Kind 01 feeds dissolve into nothing but warmed-over Bitcoin memes, GM notes, notifications from the OtherStuff, and Things Copied from X.

The problem of barren, intellectually-emptying Kind 01 feeds is further exacerbated by the fact that new entrants to the Nostrverse find it increasingly easy to "find good follows", but they're all only finding the same follows: whoever is on the trending list.
## The See-Nothings
I keep complaining about this, but the responses I get are generally unhelpful. They are:
* mockery -- Oh, Miss Hoity-Toity wants more attention!
* insults -- Nobody is talking to you because you are boring and stupid, and nobody likes you.
* clueless -- You should try replying to other people, then they might reply to you.
* or they tell me to just stop looking at the list, if it upsets me.

What people are missing, by telling me to just not look at the trending lists, is that the lists are a statistic of what real humans are looking at, on Nostr. The bizarrely-high concentration of npubs, on the list, so that their entries show up multiple times, suggests that what people are primarily looking at... is the trending list.
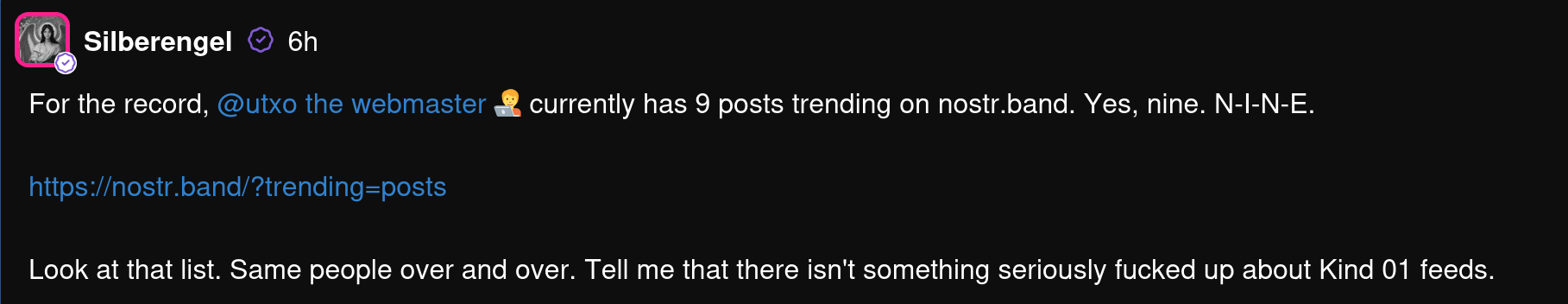
Either directly, because they use a client that has that built in, or indirectly, as they have been onboarded with the lists or told to "just follow the people I follow", which leads to a steadily-rising concentration of follows. This concentrating effect is accelerating.
The newly-popular WoT (web of trust) relays further exacerbate this effect, as they put a premium on the npubs that have the highest WoT score, which -- surprise, surprise! -- are the same people as on the trending list.
And this is why everyone on the trending list insists Nostr is a fun, happening place, full of human interaction. A place where replying reverently to Jack and posting GM religiously will make you a sought-after conversant. It is that place. For them.
In fact, they've reached that glorious state of #PeakSocialMedia, where they have become famous for being famous, and no longer have to even pretend to be trying to appeal to anyone with their content. They can post literal garbage, and their ~~fans~~ ~~groupies~~ ~~sycophants~~ commentariat will cheer them on, and flood their replies with ardent encouragement. Less because those other npubs actually cared about what they posted, than because they are hoping to pick up new followers in those threads, since they know that everyone is looking at those threads, because those threads are trending.
It's a pyramid scheme of following.
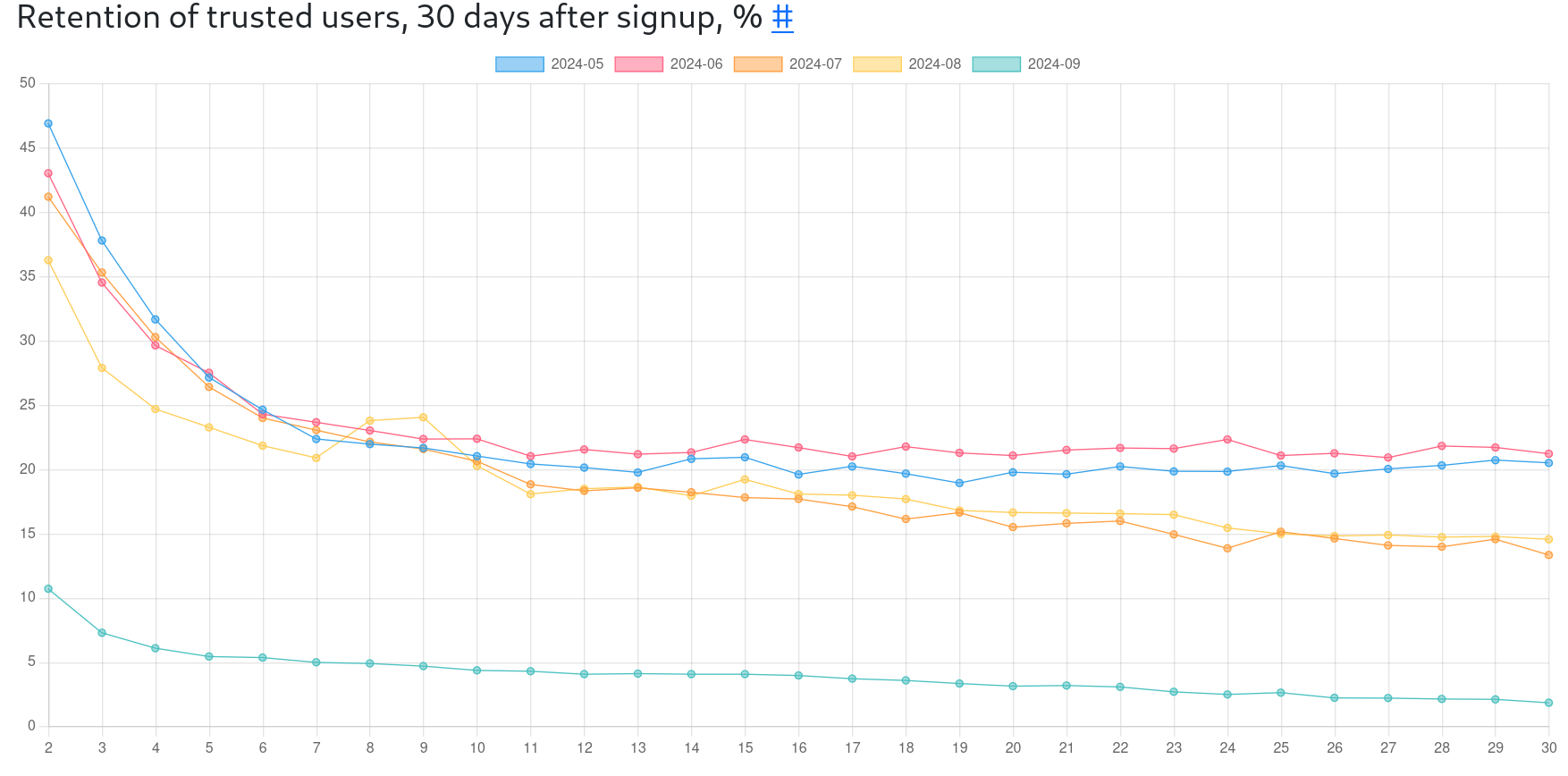
For the rest of us... the vast majority of us... that blue line at the bottom is mostly how it feels.
## The trend is to trending.
What we no longer have, is people looking directly at relay feeds, to find new people, or even their own follow list feeds, to see npubs they've already subscribed to. Even when people follow me, they usually don't respond until I'm trending, which suggests that they're also seeing me on the trending list because that is what they're primarily looking at. This is why, as soon as you get on the trending list, your replies explode. And your replies will be concentrated in a hardcore few, otherwise.
Those few are the reason I keep coming back, but as they're also often chatting with me off-Nostr, I am facing the question of: _Why bother with Nostr microblogging?_
This is the question I am struggling with. If kind 01 isn't for plebs chatting, anymore, (and it increasingly isn't) then it's mostly a sort of bulletin board, where we post notifications of items we've added in OtherStuff clients, or make announcements of meetups, software releases, or conferences. This, however, is compounding the dullness of the feeds and turning it into a sort of "info flyer", except for a lucky few. But, perhaps, I am simply a #NostrBoomer, who is failing to move with the times and get with the program.

I'm slowly reaching the conclusion that Kind 01 in an open, centralized market of notes, will always coalesce around a small subset of #NostrElite and turn into a largely passive form of entertainment, or a frustratingly lonely place, for everyone else. There can only be so many people talking, at once, in a public square.
The only movement I currently see, that might end the slow slide of Kind 01 into irrelevance and tedium, is to create lots of smaller, public squares, through single-relay communities. This has been such a long time, in coming, and has been resisted by client devs so ferociously, that I worry that it's merely an attempt to close the barn door after the npubs have escaped.
I sincerely hope to be proven wrong, though. Perhaps the relay devs, who have valiantly taken up the fight, will #SaveKind01. We shall see.
-

@ a39d19ec:3d88f61e
2024-10-28 18:44:55
##### What do you even print with it besides decorative objects?
This kind of question still is a common one when talking about 3d printing.
With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot.
Let me start the series with a nice little print consisting of two parts.
## Laptop riser
There are many designs of laptop risers available online. But I like that the parts are small and interlocking, so that the are always together when not in use. The riser fits all laptops in our house. Particularly when working in Fusion360 my laptop needs lots of fresh air.
I use the raiser regularly about 3 times a week. Sadly I don't know where I downloaded it from, so I cannot provide a link to it.

-

@ 8d34bd24:414be32b
2024-10-27 22:30:18
NOTE: *This article has some details that are specific to America, but the overall principles are applicable to all, and I believe it will be useful for all Christians.*
When it comes to things like voting, Christians tend to err to one of two extremes and seem to find difficulty finding the right balance as defined by God. Some Christians refuse to vote or get involved with politics at all. They don’t want to dirty themselves with politics. They know that their true home is heaven, so they don’t seem to care much for the nations they live in. On the other hand, some Christians are so focused on politics fixing everything and creating heaven on earth that they can become idolatrous lifting up politicians as a kind of savior.
In this article, I’m going to address both extremes, using the Bible, and hopefully help you find a Biblical balance.
## Seek the Welfare of the City Where I Have Sent You
As Christians we are just passing through our time on earth. Our true, eternal home, our true citizenship, is in heaven. That doesn’t mean that we shouldn’t care what happens on earth. We shouldn’t be like the old saying, “some Christians are so heavenly minded that they aren’t any earthly good.” I think Christians should organize our time here on earth kind of like the Israelites were commanded to live during their 70 year exile in Babylon and Persia.
> Now these are the words of the letter which Jeremiah the prophet sent from Jerusalem to the rest of the elders of the exile, the priests, the prophets and all the people whom Nebuchadnezzar had taken into exile from Jerusalem to Babylon. (Jeremiah 29:1)
What did God say to the Israelites about how they should live their life in Babylon?
> “Thus says the Lord of hosts, the God of Israel, to all the exiles whom I have sent into exile from Jerusalem to Babylon, ‘Build houses and live in them; and plant gardens and eat their produce. Take wives and become the fathers of sons and daughters, and take wives for your sons and give your daughters to husbands, that they may bear sons and daughters; and multiply there and do not decrease. **Seek the welfare of the city where I have sent you into exile, and pray to the Lord on its behalf; for in its welfare you will have welfare**.’ (Jeremiah 29:4-7) {emphasis mine}
Could we likewise say the same to Christians during their time on earth? “Build houses and live in them; and plant gardens and eat their produce. Take wives and become the fathers of sons and daughters, and take wives for your sons and give your daughters to husbands, that they may bear sons and daughters; and multiply there and do not decrease. Seek the welfare of the city, state, or nation where I have sent you to live for a short while, and pray to the Lord on its behalf; for in its welfare you will have welfare.”
God expects us to live fruitful lives, to marry, to have many children (multiply), and to raise them up to do the same. He also wants us to seek the welfare of the city, state, and nation where God has put us. In a city, state, or nation with democratic elections, the best way to seek its welfare is to vote for honest candidates who support godly principles. We rightly understand that in our ungodly world there are no perfect candidates. It can even be hard to find mostly honest and mostly godly candidates, but we should seek to elect the best that is available. Why are we told to do this? We are told that “*for in its welfare you will have welfare*.” When we fail to vote, to teach our kids or support good schools, to live productive lives, and to generally live Godly lives, we WILL see the decline of our cities, states, and nations. We will pay the price.
We are seeing exactly that decline because Christians have pulled out (and were pushed out) of the positions that influence the culture. We don’t have enough godly teachers, journalists, professors, advisors, economists, and politicians. We have given up the culture to those who oppose God, His people, and His commands.
We are paying the price for withdrawing into the safety of our churches and leaving the world to the wolves.
## Political Religion
Of course we also have an opposite extreme. We have some Christians that are too focused on politics and power. They spend all of their time and energy on political endeavors and very little, to none, on sharing the Gospel and being a godly example. Many act like they think a political candidate is going to save them from the culture, the media, the bureaucracy, or the government. They forget that there is only one Savior — the Lord Jesus Christ. They forget that God said things will get worse before they get better. They make idols out of politicians and religions out of political parties.
> No servant can serve two masters; for either he will hate the one and love the other, or else he will be devoted to one and despise the other. You cannot serve God and wealth.” (Luke 16:13)
Although this verse is specifically talking about being obsessed with wealth, it is applicable to anything that takes our focus, attention, and especially our worship away from God.
When a person spends all of their time serving one candidate or party and little to no time serving God, they have chosen to serve another god and are guilty, even if inadvertently and unintentionally.
> You shall have no other gods before Me.
>
> You shall not make for yourself an idol, or any likeness of what is in heaven above or on the earth beneath or in the water under the earth. You shall not worship them or serve them; for I, the Lord your God, am a jealous God, visiting the iniquity of the fathers on the children, on the third and the fourth generations of those who hate Me, but showing lovingkindness to thousands, to those who love Me and keep My commandments. (Exodus 20:3-6)
When we look to a politician to save us from anything, we are making him/her a god before us. When we give our all to a political party, we are taking our heart away from God and giving it to an alternate religion.
We may not think that we make idols in our modern world. It is true that we don’t usually carve them out of wood or mold them out of gold, but we have just as many idols as the Israelites did. They just look different.
I hope you will seriously consider this next point because it may be very unpopular with many of my readers. There are lots of Christians that will throw as big, if not a bigger, fit at the desecration of the American flag than over the Bible. Nobody seems to fight to retain the pledge of allegiance more than a majority of Christians. I’d argue that the American flag has become a modern day idol and the “Pledge of Allegiance” has become a religious mantra repeated to the god of government. Look at the words of the pledge:
*I pledge allegiance to the Flag of the United States of America,\
and to the Republic for which it stands,\
one Nation under God,\
indivisible, with liberty and justice for all.*
I think the inclusion of the phrase “one Nation under God” makes Christians feel OK about this pledge originally invented by a socialist whose brother sold American flags. The important part, which is why I can’t say the pledge anymore, are the words, “I pledge allegiance to the Flag of the United States of America, and to the Republic for which it stands.” I really appreciate the principles America was founded upon, but as a Christian, I can only pledge allegiance to God. My allegiance isn’t to a flag (an idol) or the government (a god). I refuse to go through a religious ritual that includes particular stances, reciting special words, and showing undue respect. We cannot “*serve two masters*.” As Christians our master should be Christ alone. Anything that becomes more important than, or even equal to, the importance of God in our lives is idolatry. We need to get our priorities right.
## In the World, but Not of the World
As we live our lives here on earth, we need to remember our God ordained purpose and our true allegiance to God. We need to remember our citizenship[1](https://trustjesus.substack.com/p/should-christians-vote#footnote-1-150236181) and family are in heaven, not here on earth.
We want to have a positive influence on our culture, including working in influential positions and voting, but we should be most focused on personal evangelism and sharing the truth of the Bible. The best way to make a difference in our culture is to change hearts and minds through the Gospel of Jesus Christ.
> But now I come to You; and these things I speak in the world so that they may have My joy made full in themselves. **I have given them Your word; and the world has hated them, because they are not of the world**, even as I am not of the world. I do not ask You to take them out of the world, but to keep them from the evil one. **They are not of the world, even as I am not of the world**. Sanctify them in the truth; **Your word is truth**. (John 17:13-17) {emphasis mine}
Although we want to be a light in the world, we have been warned that doing so will make us not fit in. It will cause many non-Christians (and maybe a few Christians whose priorities are not right) to hate us. No matter the consequences, we need to stand on the truth of the Word of God.
Too often, because we are living with those who are of this world, we start to look and act a lot like those of the world instead of looking and acting like our Savior.
> **Do not love the world nor the things in the world**. If anyone loves the world, the love of the Father is not in him. For all that is in the world, the lust of the flesh and the lust of the eyes and the boastful pride of life, is not from the Father, but is from the world. **The world is passing away**, and also its lusts; but **the one who does the will of God lives forever**. (1 John 2:15-17) {emphasis mine}
The fact that we should not love the things of the world or take on the character of things of the world is true in every part of our lives, but since we are talking here about politics, let us discuss the way many Christians talk politics.
Many Christians talk about politics in the same manner as non-Christians — cursing, name calling, insulting, and doing whatever it takes to win, no matter whether it is moral or not. I know the “other side” cheats, lies, name-calls, etc., but we should not stoop to their level. Nobody ever won another to their point of view by cursing or name calling. There are ways to point our their errors, and even how horrific some of the things pushed are, without going so low. Jesus didn’t hold back from speaking the truth. He didn’t hesitate to point out error, but was never crude about it. We should be the same. We should shine a light in such a way that those around us see such a difference that they say something similar to what was said about the apostles:
> Now as they observed the confidence of Peter and John and understood that they were uneducated and untrained men, they were amazed, and began to recognize them as having been with Jesus. (Acts 4:13)
There should be something about our words, actions, and demeanor that amazes our opponents causing them to recognize us “*as having been with Jesus*.”
I hope this post has been helpful, truthful, and not too offensive. In so many areas it is hard to find that perfect balance and to not allow ourselves to be pulled to either extreme to the detriment of our witness and our relationship to God.
> Give no offense either to Jews or to Greeks or to the church of God; just as I also please all men in all things, not seeking my own profit but the profit of the many, **so that they may be saved**. (1 Corinthians 10:32-33) {emphasis mine}
Trust Jesus.\
\
your sister in Christ,
Christy
-

@ a39d19ec:3d88f61e
2024-10-27 10:26:03
**October's daily driver is the ana-digi Casio ABX-53 Twincept with module 1326. It features are world time, stopwatch, alarm and a databank for contacts.**

## Design
I have the gold/silver colored variant with a metal band. The watch has an analog clock and a floating display with the features listed above. Best thing is the "slider" mode that switches digital functions permanently.
## Storytime
My log tells me that i bought the watch 6 years ago on a local flea market for close to nothing. It was in a bad condition and needed a new battery and some love. Sure enough it works fine since then.
Most badass feature is that the analog hands are moved electronically not mechanically.
Fun fact is that even my wife likes the floating display. First time she saw it I heard her say "Das ist echt cool", meaning "thats really cool".
-

@ eac63075:b4988b48
2024-10-26 22:14:19
The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also [addressing her Bill No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
[(PT-BR version here)](https://www.eddieoz.com/drex-e-o-fim-do-dinheiro-fisico-no-brasil/)
## **What is a CBDC?**
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their **programmability**. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
## **Practical Example: The Case of DREX During the Pandemic**
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, [the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence](https://youtu.be/cjUz2VEk4co?feature=shared&t=484&ref=eddieoz.com), limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
## **How Does China's Social Credit System Work?**
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, [including financial behavior, criminal record, social interactions, and even online activities](https://journals.sagepub.com/doi/full/10.1177/1461444819826402?ref=eddieoz.com). This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, [they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods](https://www.businessinsider.com/china-social-credit-system-punishments-and-rewards-explained-2018-4?ref=eddieoz.com), or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
## **DREX and Bill No. 3,341/2024**
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy ([Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG](https://www.camara.leg.br/proposicoesWeb/fichadetramitacao?idProposicao=2259342&fichaAmigavel=nao&ref=eddieoz.com)) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, [Julia drafted her bill, PL No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
## **Risks and Individual Freedom**
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
## **The Relationship Between DREX and Pix**
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
## **International Precedents and Resistance to CBDC**
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
## **Bill No. 3,341/2024 and Popular Pressure**
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
## **What’s at Stake?**
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
## **A Call to Action**
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-

@ 592295cf:413a0db9
2024-10-26 13:39:00
[Week 21-10]
I thinks that Saylor is on right, don't trust verify, is bullshit
Bitcoin is a financial tool!
I think it's good for me to get away from social media once a week.
I could do things outside, like walking.
Take pictures of the landscape. The weirdest thing is when the alarm calls you up in an hour.
Fiatjaf wants a cache client. I feel like I can do it, I have the set to do it,
but nostrudel is no longer working, so it's a little murky.
Next nostrudel does not accept changes to settings
(It works now!), so maybe i can think something.
I want to make a corny chat, test, read this article.
Nostr doesn't work with a vpn because relays don't know who you are. jokes aside, some clients have difficulties.
### **I couldn't take pictures of the landscape if I didn't take the wind blades.** Small local controversy.
Missing the point of content creator. Simply for final user, Simply for the creator, new feature, no missing nothing.
I'm trying to limit everything to writing for a week. I almost did. Maybe another week can do well.
Meanwhile I updated apps like Amber and Voyager, coracle, nostrmo.
The experiment continues with open vibe following the trending of Nostr. I'm following almost 120 npub.
He'll stop, I don't know, possible he's already reached the limit.
You still can't block words on the Nostr side of Open, strange thing.
The app doesn't count the follow well, still some problem cleaning the cache seems that it doesn't need.
After a while open and close and seems updated.
I wanted to try open librarian, but I was busy sending fake zap on Nostr.
This morning i try and It keeps giving me error 500 when I try to connect to a relay.
I hate when a profile follows everyone indistinctly, why does everyone follow? and in voyage, I read with WoT setting,
I probably have to do unfollow. There must be an indication in which not include the followers of this person in the web of trust,
I would do it by default if you follow more than 600 people.
WoT on Nostr Visualized [post on stackernews](https://stacker.news/items/739477)
-

@ 8f69ac99:4f92f5fd
2024-10-25 09:49:56
O recente relatório do Banco Central Europeu, [*As Consequências Distribucionais do Bitcoin*](https://papers.ssrn.com/sol3/Delivery.cfm/4985877.pdf?abstractid=4985877&mirid=1&type=2), recicla a velha narrativa de que o Bitcoin é um activo especulactivo que causa desigualdade de riqueza sem oferecer benefícios económicos tangíveis. Os autores, Ulrich Bindseil e Jürgen Schaaf, desfilam as críticas de sempre, afirmando que o Bitcoin falhou como sistema de pagamento global e que se transformou numa bolha, enriquecendo os primeiros utilizadores à custa da sociedade. Também lançam uma pitada de alarmismo ambiental e argumentam que o Bitcoin ameaça a democracia.
Como era de esperar, o BCE continua apegado às mesmas concepções erradas que já foram desmentidas inúmeras vezes. O que este relatório não percebe, de forma espectacular, é que o Bitcoin não é apenas mais um activo; é uma tábua de salvação para aqueles desiludidos com os sistemas fiduciários inflacionários e governos corruptos. Ao longo desta análise, vamos desmontar os argumentos do BCE, expondo não só o seu profundo desconhecimento sobre o Bitcoin, mas também a ignorância gritante em relação ao seu potencial de conceder soberania financeira a milhões de pessoas em todo o mundo. O BCE retrata o Bitcoin como uma ferramenta elitista, mas ignora como as suas próprias políticas têm sistematicamente enriquecido alguns poucos à custa da maioria. Vamos então entrar no assunto.
### 1. **Deturpam o Papel do Bitcoin como Sistema de Pagamentos**
> "O Bitcoin nunca foi usado em grande escala para transacções legais no mundo real."
Que originalidade. Os autores descartam a utilidade de pagamento do Bitcoin com um gesto, mostrando que não compreendem a Lightning Network, que facilita transacções rápidas, baratas e escaláveis a nível global. Certamente, talvez os europeus ainda não estejam a comprar os seus cafés com Bitcoin, mas isso é irrelevante. O Bitcoin é uma tábua de salvação financeira em locais como El Salvador e em inúmeras outras regiões que sofrem com sistemas fiduciários em colapso.
Esta visão eurocêntrica, como se todo o mundo partilhasse das mesmas condições económicas, reflecte uma total falta de perspectiva. Os autores seleccionam dados a dedo para encaixar na sua narrativa anti-Bitcoin, enquanto convenientemente ignoram os milhões que utilizam o Bitcoin para escapar à hiperinflação e a regimes autoritários. A afirmação de que o Bitcoin não é usado para transacções "legais" é não só enganosa, como revela a sua ignorância sobre as necessidades reais de quem vive fora da sua bolha privilegiada.
---
### 2. **Deturpam o Bitcoin como activo Especulactivo**
> "O Bitcoin não gera qualquer fluxo de caixa (como o imobiliário), juros (como as obrigações) ou dividendos (como as ações)."
Parabéns, BCE, acabaram de perder o ponto fulcral do Bitcoin. Esta afirmação mostra uma falta de entendimento fundamental do que torna o Bitcoin único. Ao contrário de imóveis ou obrigações, o Bitcoin é uma forma alternativa de dinheiro—não algum esquema de rendimento passivo.
O valor do Bitcoin não depende de gerar dividendos ou juros, mas advém da sua escassez, descentralização e resistência à censura. Ao reduzir o Bitcoin a modelos de activos tradicionais, o BCE ignora o paradigma económico revolucionário que este oferece: uma escapatória aos sistemas fiduciários inflacionários, particularmente para os milhares de milhões de pessoas presas em sistemas financeiros corruptos.
Ao tentar enquadrar o Bitcoin em modelos convencionais, os autores revelam a sua preguiça intelectual. A utilidade do Bitcoin reside no seu potencial como dinheiro sólido, e não como um veículo de investimento para especuladores atrás de rendimento.
---
### 3. **Deturpam os Custos Ambientais e Sociais da Mineração**
> "A mineração de Bitcoin consome muita energia e causa danos ecológicos e sociais."
Ah sim, o argumento gasto sobre o consumo energético. Enquanto a mineração de Bitcoin realmente requer energia, os autores omitem convenientemente os enormes avanços que a indústria fez em direcção à sustentabilidade. Cada vez mais, os mineradores de Bitcoin recorrem a fontes de energia renovável e, em alguns casos, estão até a ajudar a financiar infraestruturas de energia verde.
A ironia aqui é que o BCE, uma instituição que fomenta políticas que inflam bolhas imobiliárias e de acções, de repente está preocupado com os custos sociais e ambientais. E mais, ignoram como a procura de energia barata por parte do Bitcoin incentiva realmente o desenvolvimento de soluções energéticas sustentáveis. Num mundo onde os sistemas fiduciários alimentam a ganância corporativa e a degradação ambiental, o Bitcoin está posicionado para impulsionar uma verdadeira inovação na energia verde.
---
### 4. **Visão Deturpada da Redistribuição de Riqueza**
> "Os efeitos de riqueza do Bitcoin beneficiam os primeiros utilizadores à custa dos que chegam mais tarde e dos que não o possuem."
Isto é pura comédia. Aparentemente, o BCE acabou de descobrir que os primeiros investidores em **qualquer** activo beneficiam mais do que os que chegam depois. Não é assim que os mercados funcionam? Os primeiros investidores em acções, imóveis e ouro beneficiam de forma desproporcional—mas, curiosamente, isto só se torna um problema quando se trata de Bitcoin.
O que o BCE realmente teme é que o Bitcoin democratize a riqueza de uma maneira que eles não conseguem controlar. Com o Bitcoin, não precisas de acesso privilegiado para participar. Não precisas de um corretor _XPTO_ ou de permissão dos guardiões financeiros. Ao contrário das próprias políticas do BCE—concebidas para inflacionar a riqueza dos já ricos através de bolhas imobiliárias e do mercado de acções—Bitcoin oferece um campo de jogo nivelado para qualquer pessoa com uma ligação à internet.
---
### 5. **Sensacionalismo: a Ameaça à Democracia**
> "O aumento perpétuo do preço do Bitcoin empobrece o resto da sociedade e põe em risco a democracia."
Aqui, os autores entram no melodrama, avisando que o aumento do preço do Bitcoin põe em risco a democracia. É fascinante como ignoram a verdadeira ameaça à democracia: as suas próprias políticas inflacionárias.
Na realidade, os sistemas fiduciários, através da inflação incessante e do _quantitative easing_, erodem sistematicamente a riqueza dos mais pobres e da classe média. Os ricos, com as suas carteiras de acções e imóveis, conseguem resistir à tempestade. Mas o trabalhador comum, cujo salário compra cada vez menos a cada ano, é esmagado. Se há algo que ameaça a democracia, é o poder descontrolado do BCE de desvalorizar a moeda que as pessoas usam para viver. Bitcoin, por outro lado, dá às pessoas uma reserva de valor incorruptível e descentralizada, imune aos caprichos dos banqueiros centrais.
---
### 6. **Percepção "Equivocada" da Escalabilidade do Bitcoin**
> "As transações em Bitcoin na blockchain são lentas e caras."
Esta crítica ignora a realidade do progresso tecnológico. As transacções on-chain de Bitcoin nunca foram pensadas para compras diárias—para isso é que serve a Lightning Network. Os autores agarram-se a esta crítica desactualizada, como se o Bitcoin fosse uma entidade estática que não evoluiu na última década.
Soluções de segunda camada como a Lightning Network permitem transacções quase instantâneas e de baixo custo, tornando o Bitcoin escalável de maneiras que o BCE se recusa a reconhecer. Mas porque deixar que os factos estraguem uma boa história de medo?
---
### 7. **Ignoram o Impacto Económico Global do Bitcoin**
> "O Bitcoin não tem casos de uso benéficos para a sociedade."
Esta afirmação é tão limitada que é quase impressionante. A utilidade do Bitcoin não se trata de conveniência para os ocidentais comprarem café; trata-se de sobrevivência para as pessoas em países como a Venezuela, o Líbano ou a Nigéria.
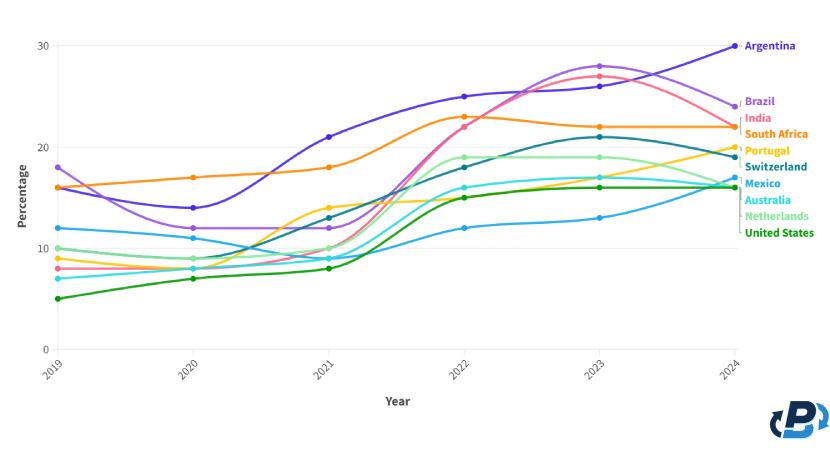
Quando as moedas locais colapsam e as pessoas não podem confiar nos seus bancos, o Bitcoin oferece uma saída. Ao descartar o impacto real de Bitcoin sobre os milhares de milhões (mais de metade da população mundial) de pessoas que vivem sob regimes opressivos e em hiperinflação, o BCE revela um embaraçoso viés ocidental e falta de empatia. O Bitcoin é mais do que apenas um activo alternativo, é uma tábua de salvação para pessoas em todo o mundo que sofrem com sistemas fiduciários falhados.
---
### Conclusão
O relatório do BCE recicla críticas desactualizadas e já desmentidas, não conseguindo ver o panorama geral. Aplica modelos financeiros antigos a uma **nova forma de dinheiro**, ignorando o potencial de Bitcoin para democratizar o acesso a um sistema financeiro justo, descentralizado e incorruptível. Enquanto os bancos centrais, como o BCE, continuam a desvalorizar moedas e a inflacionar bolhas de activos (e parece que vem ai mais...), Bitcoin oferece às pessoas um caminho para a soberania financeira.
O verdadeiro valor de Bitcoin não se encontra nas críticas superficiais e eurocêntricas do BCE. O seu valor reside na capacidade de fornecer liberdade financeira a indivíduos em todo o mundo, libertos da má gestão de governantes e banqueiros centrais. Se há algo que ameaça a democracia, é o historial do BCE de enriquecer alguns poucos à custa de muitos. Bitcoin, por outro lado, oferece um futuro mais justo—um onde são os indivíduos, e não as instituições, que têm o poder.
Alguma literatura:
- [Universidade de Cornell - Bitcoin pode impulsionar o desenvolvimento de energias renovaveis](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development)
- [Aldeias em Africa com electricidade atraves de Bitcoin](https://gridlesscompute.com/2022/09/28/21st-century-villages/)
- [Relatorio de 2023 sobre a Lightning Network da River](https://river.com/learn/files/river-lightning-report-2023.pdf)
- [Adopcao de Bitcoin por Pais](https://plasbit.com/blog/bitcoin-adoption-by-country)
---
_Photo by [Taras Chernus](https://unsplash.com/@chernus_tr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash]("https://unsplash.com/photos/man-in-teal-hoodie-with-i-love-you-text-euaivxORAm8?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_
#Bitcoin #BCE
 @ 5e5fc143:393d5a2c
2024-11-19 10:20:25Now test old reliable front end Stay tuned more later Keeping this as template long note for debugging in future as come across few NIP-33 post edit issues
@ 5e5fc143:393d5a2c
2024-11-19 10:20:25Now test old reliable front end Stay tuned more later Keeping this as template long note for debugging in future as come across few NIP-33 post edit issues @ af9c48b7:a3f7aaf4
2024-11-18 20:26:07## Chef's notes This simple, easy, no bake desert will surely be the it at you next family gathering. You can keep it a secret or share it with the crowd that this is a healthy alternative to normal pie. I think everyone will be amazed at how good it really is. ## Details - ⏲️ Prep time: 30 - 🍳 Cook time: 0 - 🍽️ Servings: 8 ## Ingredients - 1/3 cup of Heavy Cream- 0g sugar, 5.5g carbohydrates - 3/4 cup of Half and Half- 6g sugar, 3g carbohydrates - 4oz Sugar Free Cool Whip (1/2 small container) - 0g sugar, 37.5g carbohydrates - 1.5oz box (small box) of Sugar Free Instant Chocolate Pudding- 0g sugar, 32g carbohydrates - 1 Pecan Pie Crust- 24g sugar, 72g carbohydrates ## Directions 1. The total pie has 30g of sugar and 149.50g of carboydrates. So if you cut the pie into 8 equal slices, that would come to 3.75g of sugar and 18.69g carbohydrates per slice. If you decided to not eat the crust, your sugar intake would be .75 gram per slice and the carborytrates would be 9.69g per slice. Based on your objective, you could use only heavy whipping cream and no half and half to further reduce your sugar intake. 2. Mix all wet ingredients and the instant pudding until thoroughly mixed and a consistent color has been achieved. The heavy whipping cream causes the mixture to thicken the more you mix it. So, I’d recommend using an electric mixer. Once you are satisfied with the color, start mixing in the whipping cream until it has a consistent “chocolate” color thorough. Once your satisfied with the color, spoon the mixture into the pie crust, smooth the top to your liking, and then refrigerate for one hour before serving.
@ af9c48b7:a3f7aaf4
2024-11-18 20:26:07## Chef's notes This simple, easy, no bake desert will surely be the it at you next family gathering. You can keep it a secret or share it with the crowd that this is a healthy alternative to normal pie. I think everyone will be amazed at how good it really is. ## Details - ⏲️ Prep time: 30 - 🍳 Cook time: 0 - 🍽️ Servings: 8 ## Ingredients - 1/3 cup of Heavy Cream- 0g sugar, 5.5g carbohydrates - 3/4 cup of Half and Half- 6g sugar, 3g carbohydrates - 4oz Sugar Free Cool Whip (1/2 small container) - 0g sugar, 37.5g carbohydrates - 1.5oz box (small box) of Sugar Free Instant Chocolate Pudding- 0g sugar, 32g carbohydrates - 1 Pecan Pie Crust- 24g sugar, 72g carbohydrates ## Directions 1. The total pie has 30g of sugar and 149.50g of carboydrates. So if you cut the pie into 8 equal slices, that would come to 3.75g of sugar and 18.69g carbohydrates per slice. If you decided to not eat the crust, your sugar intake would be .75 gram per slice and the carborytrates would be 9.69g per slice. Based on your objective, you could use only heavy whipping cream and no half and half to further reduce your sugar intake. 2. Mix all wet ingredients and the instant pudding until thoroughly mixed and a consistent color has been achieved. The heavy whipping cream causes the mixture to thicken the more you mix it. So, I’d recommend using an electric mixer. Once you are satisfied with the color, start mixing in the whipping cream until it has a consistent “chocolate” color thorough. Once your satisfied with the color, spoon the mixture into the pie crust, smooth the top to your liking, and then refrigerate for one hour before serving. @ a39d19ec:3d88f61e
2024-11-17 10:48:56This week's functional 3d print is the "Dino Clip".  ## Dino Clip I printed it some years ago for my son, so he would have his own clip for cereal bags. Now it is used to hold a bag of dog food close. The design by "Sneaks" is a so called "print in place". This means that the whole clip with moving parts is printed in one part, without the need for assembly after the print.  The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags. Link to the file at [Printables](https://www.printables.com/model/64493-dino-clip-mechanical-cam-chip-clip-print-in-place)
@ a39d19ec:3d88f61e
2024-11-17 10:48:56This week's functional 3d print is the "Dino Clip".  ## Dino Clip I printed it some years ago for my son, so he would have his own clip for cereal bags. Now it is used to hold a bag of dog food close. The design by "Sneaks" is a so called "print in place". This means that the whole clip with moving parts is printed in one part, without the need for assembly after the print.  The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags. Link to the file at [Printables](https://www.printables.com/model/64493-dino-clip-mechanical-cam-chip-clip-print-in-place) @ fd208ee8:0fd927c1
2024-11-17 09:14:56You don't understand how insidious open-borders propaganda is, until you realize that _it's an attempt to remove all differentiating traits from humans_. They call this "strengthening individuality by removing nationality" (hello, newspeak), but what makes humans individual is their particular collection of traits, and nationality (and ethnicity, religion, etc. -- nationality is just the first domino they want to topple) is one of those.  Humans are not blank slates. Like DNA or physiognomy, our personalities are differing jumbles of cultural "letters". Each person selects consciously and subconsciously from amongst these letters, adding to or rejecting them, amplifying or suppressing them, twisting or combining them, building on top of them... and that's what makes you into You. Open borders is an attempt to reduce the number of cultural letters you can build your "You" out of. If you take away the word "German", I am not liberated. There is simply one less adjective, with which I can describe myself. You have merely eradicated information, crippled language, and reduced my choices. I can then no longer define myself according to "German things", but I can also no longer define myself in opposition to German things. ## Enter the Borg  We are easier to control and brainwash and persecute, if we are centralized and homogenized. As if the entire world were one, big prison and we were all forced to undergo the same education, wear the same clothes, follow the same rules, eat the same foods, enjoy the same entertainment, live the same lifestyle, share the same diseases and cures, enjoy the same lockdowns, join in the same cancel culture, fight the same wars. That is what globalization brings. That is the end game of Open Borders: * No more cultural evolution or revolution. * Genes, but no memes. * You can go everywhere, but everywhere is the same, so you just stay home. * You can meet people from all over, but they are all the same, so you just don't bother. * One mass of humanity, that can be easily molded and manipulated.
@ fd208ee8:0fd927c1
2024-11-17 09:14:56You don't understand how insidious open-borders propaganda is, until you realize that _it's an attempt to remove all differentiating traits from humans_. They call this "strengthening individuality by removing nationality" (hello, newspeak), but what makes humans individual is their particular collection of traits, and nationality (and ethnicity, religion, etc. -- nationality is just the first domino they want to topple) is one of those.  Humans are not blank slates. Like DNA or physiognomy, our personalities are differing jumbles of cultural "letters". Each person selects consciously and subconsciously from amongst these letters, adding to or rejecting them, amplifying or suppressing them, twisting or combining them, building on top of them... and that's what makes you into You. Open borders is an attempt to reduce the number of cultural letters you can build your "You" out of. If you take away the word "German", I am not liberated. There is simply one less adjective, with which I can describe myself. You have merely eradicated information, crippled language, and reduced my choices. I can then no longer define myself according to "German things", but I can also no longer define myself in opposition to German things. ## Enter the Borg  We are easier to control and brainwash and persecute, if we are centralized and homogenized. As if the entire world were one, big prison and we were all forced to undergo the same education, wear the same clothes, follow the same rules, eat the same foods, enjoy the same entertainment, live the same lifestyle, share the same diseases and cures, enjoy the same lockdowns, join in the same cancel culture, fight the same wars. That is what globalization brings. That is the end game of Open Borders: * No more cultural evolution or revolution. * Genes, but no memes. * You can go everywhere, but everywhere is the same, so you just stay home. * You can meet people from all over, but they are all the same, so you just don't bother. * One mass of humanity, that can be easily molded and manipulated. @ 13351007:eccd002a
2024-11-13 16:34:01[{"_id":"5478974e-5e9b-4ccc-8cee-8485f60838ef","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":202.86468,"amountCurrency":"xmr","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:34:01.270Z"},{"_id":"5478974e-5e9b-4ccc-8cee-8485f60838ef","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"5478974e-5e9b-4ccc-8cee-8485f60838ef","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":202.86468,"amountCurrency":"xmr","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:34:01.270Z"}]
@ 13351007:eccd002a
2024-11-13 16:34:01[{"_id":"5478974e-5e9b-4ccc-8cee-8485f60838ef","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":202.86468,"amountCurrency":"xmr","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:34:01.270Z"},{"_id":"5478974e-5e9b-4ccc-8cee-8485f60838ef","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"5478974e-5e9b-4ccc-8cee-8485f60838ef","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":202.86468,"amountCurrency":"xmr","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:34:01.270Z"}] @ 13351007:eccd002a
2024-11-13 16:33:01[{"_id":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.03,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:33:01.332Z"},{"_id":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.03,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:33:01.332Z"}]
@ 13351007:eccd002a
2024-11-13 16:33:01[{"_id":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.03,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:33:01.332Z"},{"_id":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"662f7f07-a7ef-4f29-9bdb-6d199e7dac2c","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.03,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:33:01.332Z"}] @ 13351007:eccd002a
2024-11-13 16:32:01[{"_id":"a740e2cb-8940-4d1b-bf4c-271de778bd77","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.02,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:32:01.342Z"},{"_id":"a740e2cb-8940-4d1b-bf4c-271de778bd77","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"a740e2cb-8940-4d1b-bf4c-271de778bd77","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.02,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:32:01.342Z"}]
@ 13351007:eccd002a
2024-11-13 16:32:01[{"_id":"a740e2cb-8940-4d1b-bf4c-271de778bd77","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.02,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:32:01.342Z"},{"_id":"a740e2cb-8940-4d1b-bf4c-271de778bd77","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"a740e2cb-8940-4d1b-bf4c-271de778bd77","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.02,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:32:01.342Z"}] @ 13351007:eccd002a
2024-11-13 16:31:10[{"_id":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.01,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:31:10.741Z"},{"_id":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.01,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:31:10.741Z"}]
@ 13351007:eccd002a
2024-11-13 16:31:10[{"_id":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.01,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:31:10.741Z"},{"_id":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"6b08a49c-6812-4e79-8f5b-0a1eff7b8846","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500.01,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T16:31:10.741Z"}] @ 13351007:eccd002a
2024-11-13 14:50:53[{"_id":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T14:50:53.706Z"},{"_id":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T14:50:53.706Z"}]
@ 13351007:eccd002a
2024-11-13 14:50:53[{"_id":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T14:50:53.706Z"},{"_id":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"c8b5c272-899c-4258-8ed8-d39d8b1f2802","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":500,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T14:50:53.706Z"}] @ 13351007:eccd002a
2024-11-13 09:17:38[{"_id":"f61999d4-6dd5-4593-9798-17980ecebd22","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100.02,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T09:17:38.105Z"},{"_id":"f61999d4-6dd5-4593-9798-17980ecebd22","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"f61999d4-6dd5-4593-9798-17980ecebd22","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100.02,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T09:17:38.105Z"}]
@ 13351007:eccd002a
2024-11-13 09:17:38[{"_id":"f61999d4-6dd5-4593-9798-17980ecebd22","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100.02,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T09:17:38.105Z"},{"_id":"f61999d4-6dd5-4593-9798-17980ecebd22","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"f61999d4-6dd5-4593-9798-17980ecebd22","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100.02,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T09:17:38.105Z"}] @ 13351007:eccd002a
2024-11-13 08:02:18[{"_id":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":102,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T08:02:18.346Z"},{"_id":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":102,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T08:02:18.346Z"}]
@ 13351007:eccd002a
2024-11-13 08:02:18[{"_id":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","user_id":"b34f99f110bb65ff4b5527f8fb1d015951a3038370fd95adc34d81d9006b0fcc","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":102,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T08:02:18.346Z"},{"_id":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","user_id":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","tradingPartner":"liam","tradeId":"c178a999-25e0-4bf5-b478-b6f22ae9bfbd","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":102,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T08:02:18.346Z"}] @ 13351007:eccd002a
2024-11-13 07:54:13[{"_id":"b99131ca-10fb-48fd-be00-04aee70efd55","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.400Z"},{"_id":"b99131ca-10fb-48fd-be00-04aee70efd55","tradingPartner":"liam","tradeId":"b99131ca-10fb-48fd-be00-04aee70efd55","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.400Z"}]
@ 13351007:eccd002a
2024-11-13 07:54:13[{"_id":"b99131ca-10fb-48fd-be00-04aee70efd55","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.400Z"},{"_id":"b99131ca-10fb-48fd-be00-04aee70efd55","tradingPartner":"liam","tradeId":"b99131ca-10fb-48fd-be00-04aee70efd55","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":100,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.400Z"}] @ 13351007:eccd002a
2024-11-13 07:54:13[{"_id":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":101,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.286Z"},{"_id":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","tradingPartner":"liam","tradeId":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":101,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.286Z"}]
@ 13351007:eccd002a
2024-11-13 07:54:13[{"_id":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":101,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.286Z"},{"_id":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","tradingPartner":"liam","tradeId":"a8fd0883-c47a-4eba-bf4c-61ff15f836ff","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":101,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T07:54:13.286Z"}] @ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"d12af7f8-9fad-4718-85d2-71de3e1ab22f","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":1,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.527Z"}
@ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"d12af7f8-9fad-4718-85d2-71de3e1ab22f","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":1,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.527Z"} @ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"45961f60-af28-49a7-8285-39d46a04ae04","tradingPartner":"liam","adId":"10df86b1-657c-4065-b5c8-d6f6bbe64a7b","adPublisher":"f462d21e10163eb0a403aec6b93ac57ec2f1b9455473e99304f571a51390b6b1","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":170.27,"amount":1.5,"amountCurrency":"fiat","paymentMethodCode":"VENMO","currencyCode":"USD","country":"United Kingdom","countryCode":"GB","paymentMethodDetail":"best rates really","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.127Z"}
@ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"45961f60-af28-49a7-8285-39d46a04ae04","tradingPartner":"liam","adId":"10df86b1-657c-4065-b5c8-d6f6bbe64a7b","adPublisher":"f462d21e10163eb0a403aec6b93ac57ec2f1b9455473e99304f571a51390b6b1","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":170.27,"amount":1.5,"amountCurrency":"fiat","paymentMethodCode":"VENMO","currencyCode":"USD","country":"United Kingdom","countryCode":"GB","paymentMethodDetail":"best rates really","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.127Z"} @ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"79c3b4de-fb00-40e6-82b4-9c8474d90c43","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":1.6,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.210Z"}
@ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"79c3b4de-fb00-40e6-82b4-9c8474d90c43","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":1.6,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.210Z"} @ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"6189965d-885f-44a5-8283-236809f90bb4","tradingPartner":"liam","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":2,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.193Z"}
@ 13351007:eccd002a
2024-11-13 06:54:35{"_id":"6189965d-885f-44a5-8283-236809f90bb4","tradingPartner":"liam","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_BUY","adTypeReal":"ONLINE_SELL","price":169.05,"amount":2,"amountCurrency":"fiat","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:35.193Z"} @ 13351007:eccd002a
2024-11-13 06:54:34{"_id":"fad63d53-f555-429e-916a-d2ea8968552d","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":20,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:34.754Z"}
@ 13351007:eccd002a
2024-11-13 06:54:34{"_id":"fad63d53-f555-429e-916a-d2ea8968552d","tradingPartner":"hank","adId":"493d4425-5a4b-46b6-b1a4-2e1266ea1246","adPublisher":"1eb966a6a0218aba520aaac93be7dd8bf3830fc7710bc80caea3a6a5e3eddf94","adType":"ONLINE_SELL","adTypeReal":"ONLINE_SELL","price":169.05,"amount":20,"amountCurrency":"fiat","buyerSettlementAddress":"888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H","paymentMethodCode":"NATIONAL_BANK","currencyCode":"USD","country":"United States of America","countryCode":"US","paymentMethodDetail":"fast and best trader","msg":"","accountInfo":"","action":"open","added":"2024-11-13T06:54:34.754Z"} @ 13351007:eccd002a
2024-11-12 17:32:12just testing with p tag
@ 13351007:eccd002a
2024-11-12 17:32:12just testing with p tag @ 13351007:eccd002a
2024-11-12 16:33:39just testing with p tag
@ 13351007:eccd002a
2024-11-12 16:33:39just testing with p tag @ 13351007:eccd002a
2024-11-12 15:44:07just testing
@ 13351007:eccd002a
2024-11-12 15:44:07just testing @ 6be5cc06:5259daf0
2024-11-12 03:11:11### Primeiramente, o que é mempool? Abreviação de memory pool (ou *"pool de memória"*) a mempool é uma espécie de fila onde as transações de Bitcoin ficam temporariamente armazenadas antes de serem confirmadas e incluídas em um bloco na blockchain. Quando você realiza uma transação em uma rede blockchain, essa transação precisa ser validada e confirmada pelos mineradores (ou validadores). Porém, ela não é processada instantaneamente. Primeiro, ela vai para a mempool, onde aguarda até que um minerador a selecione para incluir no próximo bloco. É assim: * Você envia uma transação, ela é transmitida para a rede e vai parar na mempool de vários nós (computadores) que suportam a rede blockchain. * As transações na mempool são organizadas pela taxa de transação que foi anexada. Quanto maior a taxa, mais rápido os mineradores tendem a escolher essa transação para incluí-la em um bloco, pois isso aumenta os ganhos deles. * Os mineradores pegam as transações da mempool, criam um bloco com elas e, ao minerar (confirmar) esse bloco, as transações saem da mempool e entram na blockchain. Aqui irei usar o site [mempool.emzy.de](https://mempool.emzy.de/) como referência, mas é importante entender que sites de mempool são representações visuais da mempool de um nó específico e não *a mempool do Bitcoin* em si. Ela não é centralizada, cada nó da rede mantém a sua própria versão da mempool. Assim, ela pode variar de um nó para outro. Esses sites ajudam a visualizar dados sobre transações e taxas. É uma boa prática usar **VPN** ou **Tor** ao acessar tais sites se você estiver verificando uma transação específica sua, pois sua privacidade pode ficar comprometida se o site registrar esses dados. Se você estiver repetidamente acessando-o para monitorar a confirmação de uma transação, alguém pode conseguir correlacionar o endereço IP com essa atividade e revelar uma conexão indireta com o endereço da transação. Dito isso... ### Como interpretar a mempool? Vamos dividir isso em partes para fins didáticos. --- 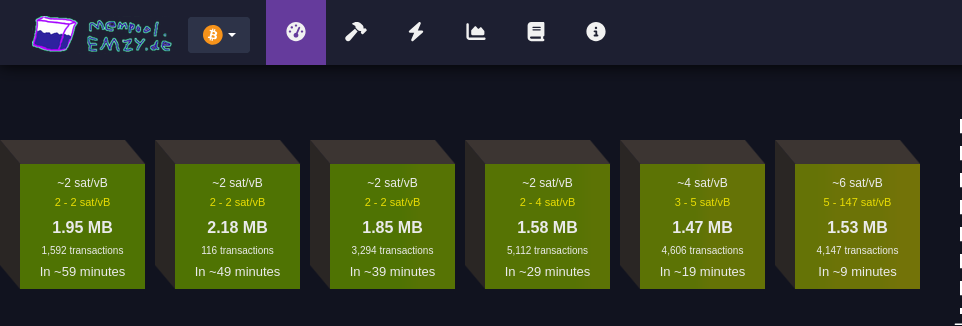 #### Faixa de taxas Cada bloco verde representa uma faixa de taxa medida em satoshis por vByte (sats/vB). Essa unidade de medida representa o valor pago por byte ocupado pela transação. Quanto maior a taxa paga por uma transação, mais rápido ela tende a ser confirmada. Quanto maior a transação em bytes, mais você precisa pagar para que ela seja confirmada. Cada transação Bitcoin consiste em *entradas* e *saídas* (*inputs* e *outputs*): * **Entradas** são referências a transações anteriores que estão sendo gastas, e cada entrada inclui informações como o endereço de origem, a assinatura (que valida a transação e pode variar de tamanho dependendo da complexidade da chave e do método de assinatura utilizado (como SegWit, que é mais eficiente). Quanto mais complexa a assinatura, maior será o tamanho em bytes) e outros dados. Quanto mais entradas uma transação tiver, maior será seu tamanho. * **Saídas** representam o destino do Bitcoin, e quanto mais saídas, maior será o tamanho da transação. Embora as saídas ocupem menos espaço em bytes do que as entradas. Ex.: * ~4 sat/vB: Indica uma taxa média. Significa que, em média, as transações estão sendo processadas a 4 satoshis por vByte; * 3-5 sat/vB: Isso significa que as transações estão sendo processadas com uma taxa entre 3 e 5 satoshis por vByte. #### MB Simplesmente o tamanho do bloco medido em megabytes :) #### Número de transações Essa seção informa quantas transações estão aguardando confirmação para cada faixa de taxa (bloco). Quanto maior o número de transações, maior a demanda pela faixa de taxa especificada. #### Tempo estimado para confirmação Aqui é mostrado o tempo médio de espera para transações que pagam taxas dentro da faixa especificada. Se você pagar uma taxa maior, a transação será confirmada mais rapidamente; uma taxa menor significa que a transação pode levar mais tempo para ser confirmada, especialmente se a rede estiver congestionada. --- 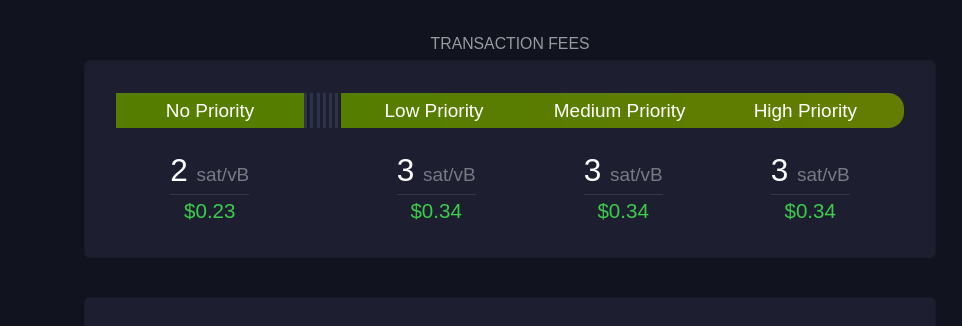 Esta seção mostra sugestões de taxa em diferentes níveis de prioridade para os usuários: #### Sem Prioridade Exibe a taxa mínima necessária para transações que não precisam de confirmação rápida. #### Prioridade Baixa Sugestão de taxa para transações que podem esperar um tempo moderado, com expectativa de confirmação em um ou dois blocos. #### Prioridade Média e Alta São as faixas de taxa recomendadas para quem precisa que a transação seja confirmada rapidamente. "Prioridade Alta" paga uma taxa maior, garantindo que a transação seja incluída no próximo bloco. --- 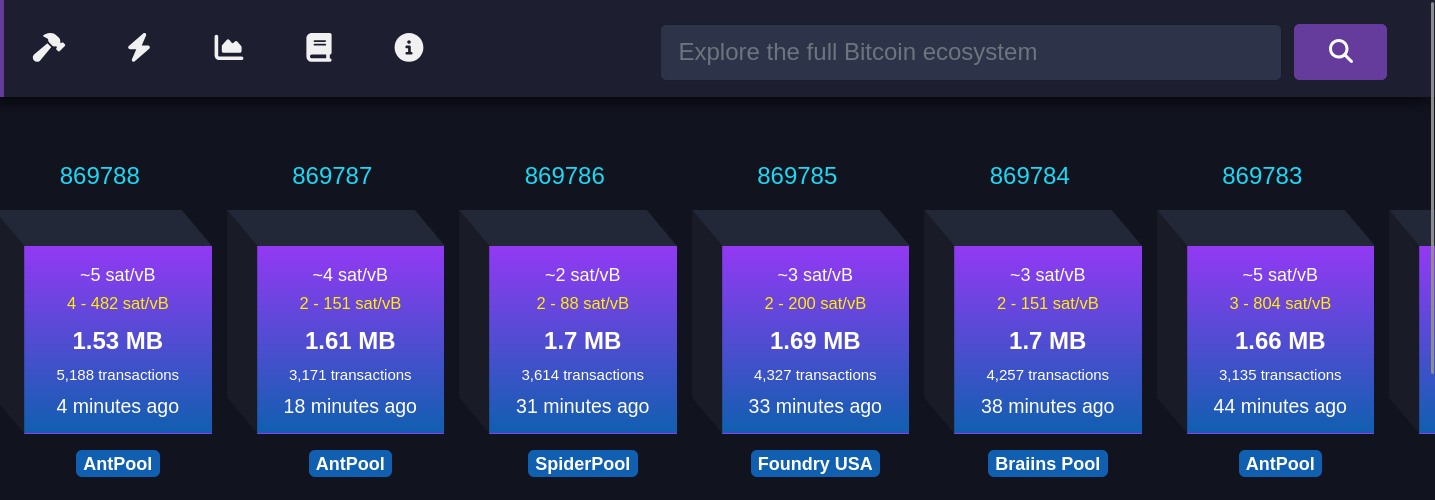 Cada bloco roxo representa um bloco recém-minerado. As informações mostradas incluem: #### Taxa média paga Refere-se à taxa média em satoshis/vB paga por todas as transações incluídas em um bloco recém-minerado. Isso reflete o valor médio que os usuários estão dispostos a pagar para que suas transações sejam confirmadas rapidamente. #### Número de transações Este número indica quantas transações foram processadas no bloco minerado. O tamanho do bloco é limitado, então, quanto maior o número de transações, menor será o espaço disponível para novas transações, o que pode influenciar as taxas de transação. #### Tempo desde a mineração Esta métrica informa quanto tempo se passou desde que o bloco foi minerado e adicionado à blockchain. #### Pool de mineração Exibe o nome do pool de mineração que minerou o bloco, como AntPool. Grandes pools de mineração têm mais chances de minerar blocos regularmente devido ao alto hashrate (medida da capacidade computacional utilizada pelos mineradores) que possuem. --- 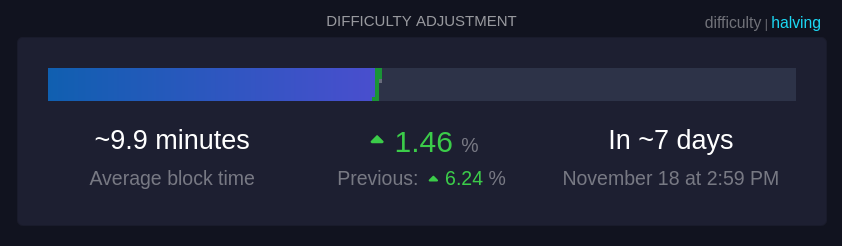 Essa seção mostra informações sobre o ajuste de dificuldade, que ocorre aproximadamente a cada duas semanas. #### Tempo médio dos blocos (~9,9 minutos): Este é o tempo médio atual para minerar um bloco na rede. A meta da rede é manter o tempo de bloco em cerca de 10 minutos; um tempo menor indica um aumento na taxa de hash, ou seja, que mais poder computacional foi adicionado à rede. #### Mudança de dificuldade (+1,46%): A dificuldade ajusta-se a cada 2016 blocos para manter o tempo médio de bloco próximo de 10 minutos. Um aumento na dificuldade, como +1,46%, indica que a mineração ficou mais difícil devido ao aumento do hashrate, enquanto uma redução na dificuldade indica que o hashrate diminuiu. #### Tempo até o próximo ajuste: É o tempo previsto até o próximo ajuste de dificuldade (7 dias, nesse caso), o que é crucial para manter a rede estável e garantir a segurança e a regularidade do processo de mineração. --- 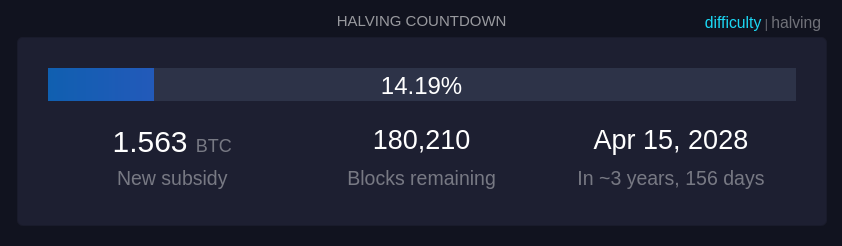 Quanto tempo demora até o próximo halving, um evento no Bitcoin que ocorre aproximadamente a cada 210.000 blocos minerados, ou cerca de quatro anos. Durante o halving, a recompensa que os mineradores recebem por adicionar um novo bloco à blockchain é reduzida pela metade. --- 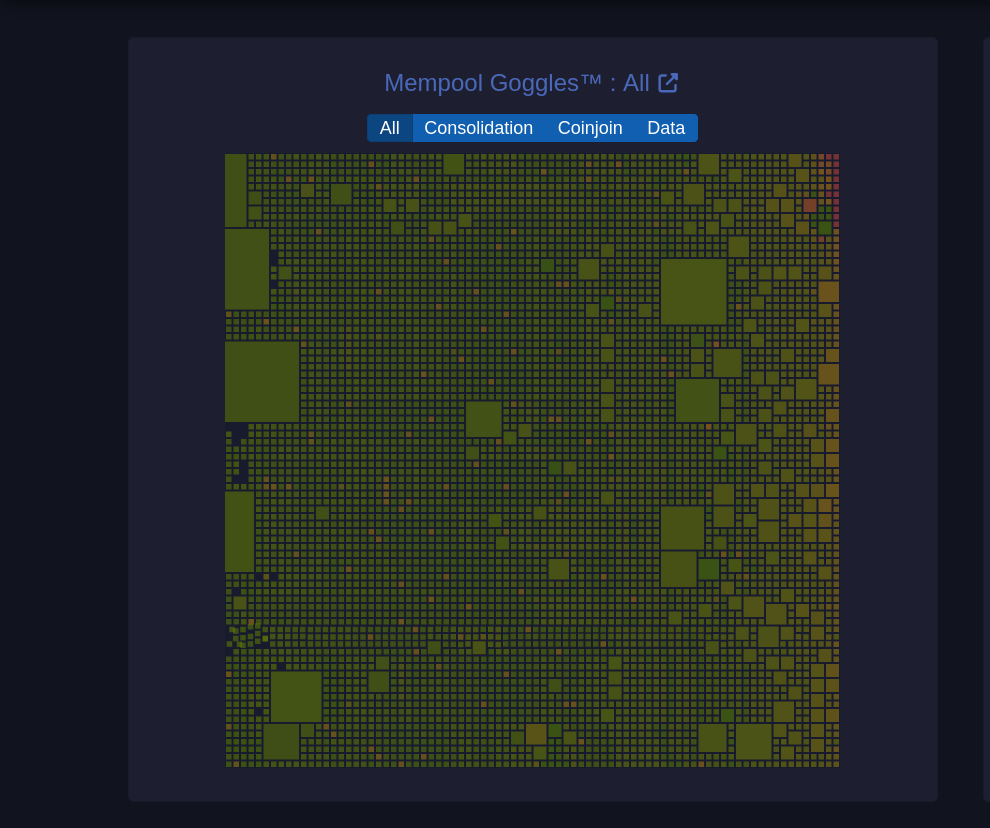 Um diagrama visual da mempool que mostra o estado das transações pendentes na rede. #### Tamanhos de blocos O tamanho de cada quadrado representa o tamanho da transação em bytes. **Filtros (Consolidação, Coinjoin, Dados):** Permite visualizar categorias específicas de transações: * **Consolidação**: Transações de consolidação agrupam pequenos UTXOs em um único UTXO maior para simplificar e baratear futuras transações. (UTXOs merecem um artigo dedicado) * **Coinjoin**: Transações CoinJoin são usadas para melhorar a privacidade, misturando transações de vários usuários em uma única transação. * **Dados**: Mostra transações que contêm dados adicionais, que podem incluir informações não financeiras, como mensagens. --- 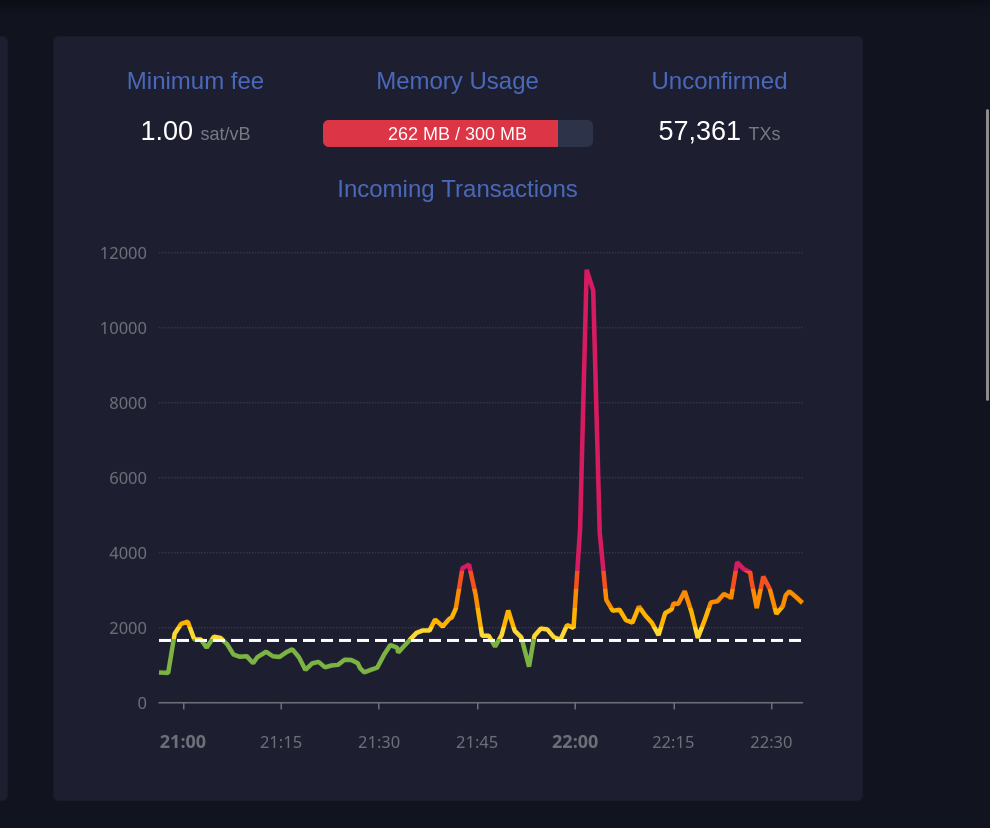 Este gráfico exibe o número de transações recebidas ao longo do tempo. #### Taxa mínima (1 sat/vB): Indica a taxa mínima atualmente aceita pela mempool. Se a mempool estiver cheia, transações que paguem menos do que a taxa mínima podem ser excluídas para dar lugar a transações de maior prioridade. #### Uso de memória (259 MB / 300 MB): A mempool tem um limite de memória. Quando está cheia, transações de taxa mais baixa podem ser descartadas para abrir espaço para aquelas com taxas mais altas, priorizando-as para inclusão em blocos. #### Transações não confirmadas (59.361): Indica o número total de transações pendentes que aguardam confirmação. Quanto maior o número de transações na mempool, maior a probabilidade de que as taxas aumentem para garantir uma confirmação mais rápida. ---  Essa seção mostra transações que foram substituídas utilizando o mecanismo RBF (Replace-By-Fee), que permite substituir uma transação com uma taxa mais alta para acelerar sua confirmação. #### TXID Este é o identificador da transação (Transaction ID), exibido parcialmente para abreviar o espaço. Cada transação tem um identificador único na blockchain. #### Previous fee Exibe a taxa de transação original paga na primeira tentativa, medida em satoshis por vByte (sat/vB). Esta taxa inicial provavelmente era baixa demais, resultando em uma demora na confirmação. #### New fee Mostra a nova taxa de transação, também em satoshis por vByte, definida para substituir a taxa anterior. Uma taxa maior aumenta as chances de inclusão rápida em um bloco. #### Status (RBF) RBF indica que a transação foi substituída utilizando o recurso "Replace-By-Fee". Isso significa que a nova transação cancelou e substituiu a original, e o minerador escolherá a transação com a taxa mais alta para incluir no próximo bloco. --- 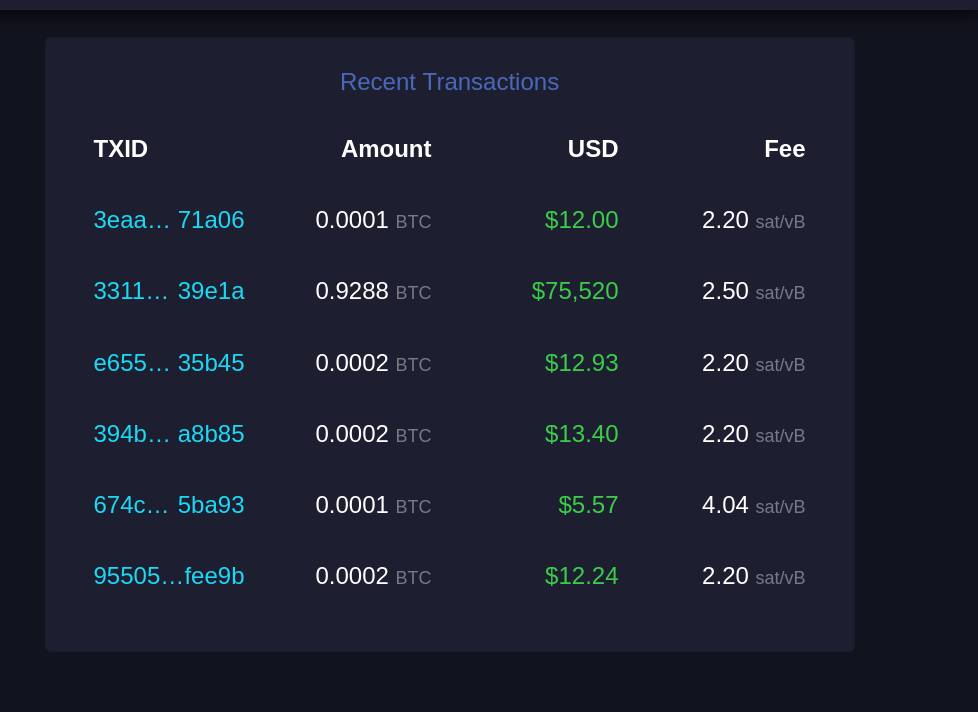 Esta seção lista transações recentes que entraram na mempool e aguardam confirmação. #### TXID Similar ao "Recent Replacements", este é o identificador único da transação. #### Amount Exibe a quantidade de Bitcoin transferida nessa transação, geralmente em frações de BTC (como 0.0001 BTC). Esta é a quantia enviada pelo remetente ao destinatário. #### USD Mostra o valor da transação em dólares americanos (USD), calculado com base na taxa de câmbio atual. Serve para dar uma ideia de quanto a transação representa em moeda fiduciária. #### Fee Exibe a taxa de transação paga, em satoshis por vByte (sat/vB). Uma taxa mais alta em relação à média aumenta a probabilidade de confirmação mais rápida, pois as transações com taxas mais elevadas são priorizadas pelos mineradores. --- E acabou. Espero que isso tenha sido útil para você e tenha agregado mais entendimento sobre esse complexo e maravilhoso mundo do Bitcoin. Se foi, considere compartilhar com alguém que precise. E se tem sugestões de melhoria, por favor, não deixe de comentar, o conhecimento está dispero na sociedade. Por fim, stay humble and stack sats!
@ 6be5cc06:5259daf0
2024-11-12 03:11:11### Primeiramente, o que é mempool? Abreviação de memory pool (ou *"pool de memória"*) a mempool é uma espécie de fila onde as transações de Bitcoin ficam temporariamente armazenadas antes de serem confirmadas e incluídas em um bloco na blockchain. Quando você realiza uma transação em uma rede blockchain, essa transação precisa ser validada e confirmada pelos mineradores (ou validadores). Porém, ela não é processada instantaneamente. Primeiro, ela vai para a mempool, onde aguarda até que um minerador a selecione para incluir no próximo bloco. É assim: * Você envia uma transação, ela é transmitida para a rede e vai parar na mempool de vários nós (computadores) que suportam a rede blockchain. * As transações na mempool são organizadas pela taxa de transação que foi anexada. Quanto maior a taxa, mais rápido os mineradores tendem a escolher essa transação para incluí-la em um bloco, pois isso aumenta os ganhos deles. * Os mineradores pegam as transações da mempool, criam um bloco com elas e, ao minerar (confirmar) esse bloco, as transações saem da mempool e entram na blockchain. Aqui irei usar o site [mempool.emzy.de](https://mempool.emzy.de/) como referência, mas é importante entender que sites de mempool são representações visuais da mempool de um nó específico e não *a mempool do Bitcoin* em si. Ela não é centralizada, cada nó da rede mantém a sua própria versão da mempool. Assim, ela pode variar de um nó para outro. Esses sites ajudam a visualizar dados sobre transações e taxas. É uma boa prática usar **VPN** ou **Tor** ao acessar tais sites se você estiver verificando uma transação específica sua, pois sua privacidade pode ficar comprometida se o site registrar esses dados. Se você estiver repetidamente acessando-o para monitorar a confirmação de uma transação, alguém pode conseguir correlacionar o endereço IP com essa atividade e revelar uma conexão indireta com o endereço da transação. Dito isso... ### Como interpretar a mempool? Vamos dividir isso em partes para fins didáticos. --- 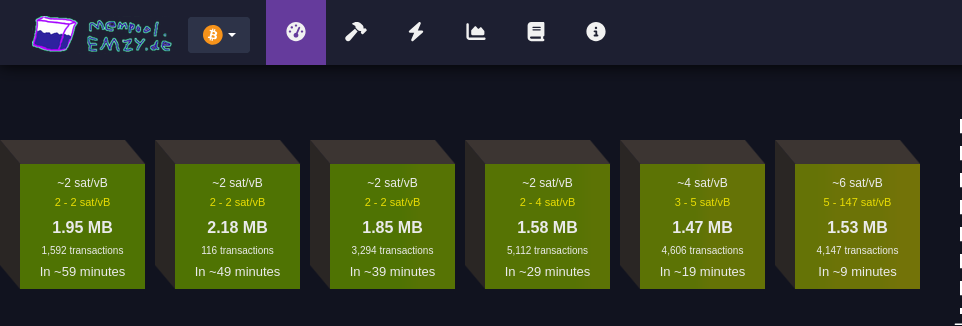 #### Faixa de taxas Cada bloco verde representa uma faixa de taxa medida em satoshis por vByte (sats/vB). Essa unidade de medida representa o valor pago por byte ocupado pela transação. Quanto maior a taxa paga por uma transação, mais rápido ela tende a ser confirmada. Quanto maior a transação em bytes, mais você precisa pagar para que ela seja confirmada. Cada transação Bitcoin consiste em *entradas* e *saídas* (*inputs* e *outputs*): * **Entradas** são referências a transações anteriores que estão sendo gastas, e cada entrada inclui informações como o endereço de origem, a assinatura (que valida a transação e pode variar de tamanho dependendo da complexidade da chave e do método de assinatura utilizado (como SegWit, que é mais eficiente). Quanto mais complexa a assinatura, maior será o tamanho em bytes) e outros dados. Quanto mais entradas uma transação tiver, maior será seu tamanho. * **Saídas** representam o destino do Bitcoin, e quanto mais saídas, maior será o tamanho da transação. Embora as saídas ocupem menos espaço em bytes do que as entradas. Ex.: * ~4 sat/vB: Indica uma taxa média. Significa que, em média, as transações estão sendo processadas a 4 satoshis por vByte; * 3-5 sat/vB: Isso significa que as transações estão sendo processadas com uma taxa entre 3 e 5 satoshis por vByte. #### MB Simplesmente o tamanho do bloco medido em megabytes :) #### Número de transações Essa seção informa quantas transações estão aguardando confirmação para cada faixa de taxa (bloco). Quanto maior o número de transações, maior a demanda pela faixa de taxa especificada. #### Tempo estimado para confirmação Aqui é mostrado o tempo médio de espera para transações que pagam taxas dentro da faixa especificada. Se você pagar uma taxa maior, a transação será confirmada mais rapidamente; uma taxa menor significa que a transação pode levar mais tempo para ser confirmada, especialmente se a rede estiver congestionada. --- 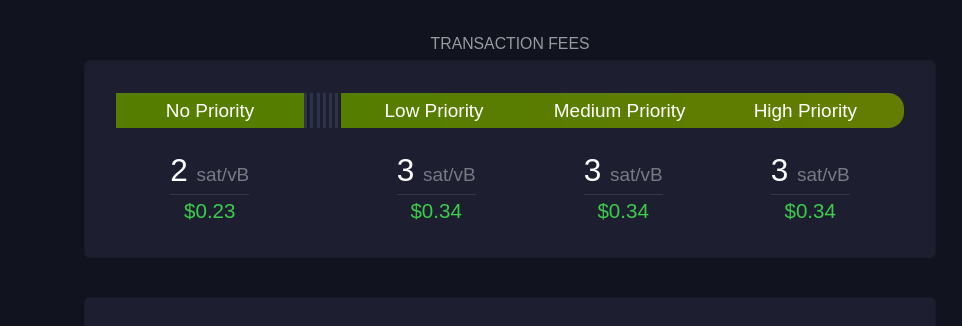 Esta seção mostra sugestões de taxa em diferentes níveis de prioridade para os usuários: #### Sem Prioridade Exibe a taxa mínima necessária para transações que não precisam de confirmação rápida. #### Prioridade Baixa Sugestão de taxa para transações que podem esperar um tempo moderado, com expectativa de confirmação em um ou dois blocos. #### Prioridade Média e Alta São as faixas de taxa recomendadas para quem precisa que a transação seja confirmada rapidamente. "Prioridade Alta" paga uma taxa maior, garantindo que a transação seja incluída no próximo bloco. --- 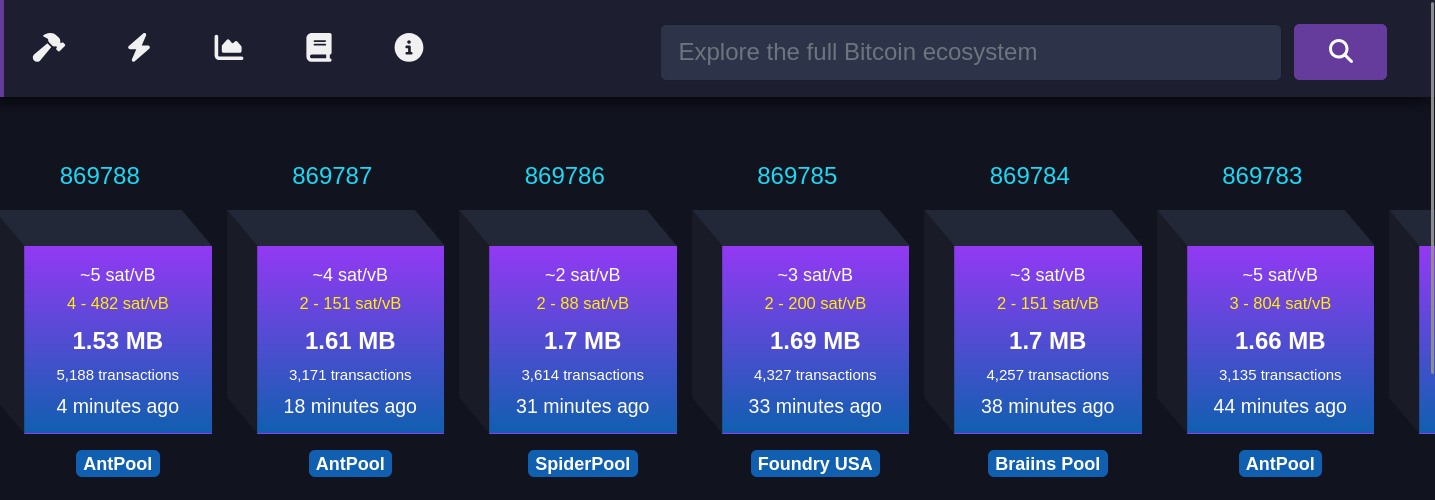 Cada bloco roxo representa um bloco recém-minerado. As informações mostradas incluem: #### Taxa média paga Refere-se à taxa média em satoshis/vB paga por todas as transações incluídas em um bloco recém-minerado. Isso reflete o valor médio que os usuários estão dispostos a pagar para que suas transações sejam confirmadas rapidamente. #### Número de transações Este número indica quantas transações foram processadas no bloco minerado. O tamanho do bloco é limitado, então, quanto maior o número de transações, menor será o espaço disponível para novas transações, o que pode influenciar as taxas de transação. #### Tempo desde a mineração Esta métrica informa quanto tempo se passou desde que o bloco foi minerado e adicionado à blockchain. #### Pool de mineração Exibe o nome do pool de mineração que minerou o bloco, como AntPool. Grandes pools de mineração têm mais chances de minerar blocos regularmente devido ao alto hashrate (medida da capacidade computacional utilizada pelos mineradores) que possuem. --- 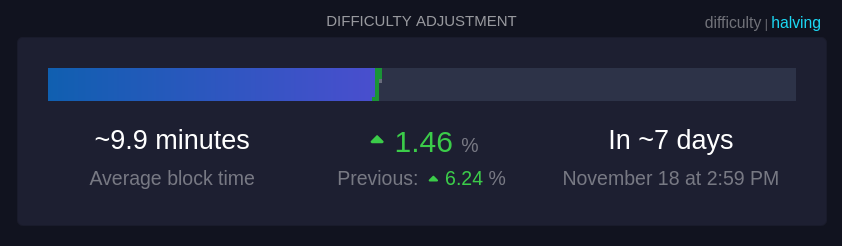 Essa seção mostra informações sobre o ajuste de dificuldade, que ocorre aproximadamente a cada duas semanas. #### Tempo médio dos blocos (~9,9 minutos): Este é o tempo médio atual para minerar um bloco na rede. A meta da rede é manter o tempo de bloco em cerca de 10 minutos; um tempo menor indica um aumento na taxa de hash, ou seja, que mais poder computacional foi adicionado à rede. #### Mudança de dificuldade (+1,46%): A dificuldade ajusta-se a cada 2016 blocos para manter o tempo médio de bloco próximo de 10 minutos. Um aumento na dificuldade, como +1,46%, indica que a mineração ficou mais difícil devido ao aumento do hashrate, enquanto uma redução na dificuldade indica que o hashrate diminuiu. #### Tempo até o próximo ajuste: É o tempo previsto até o próximo ajuste de dificuldade (7 dias, nesse caso), o que é crucial para manter a rede estável e garantir a segurança e a regularidade do processo de mineração. --- 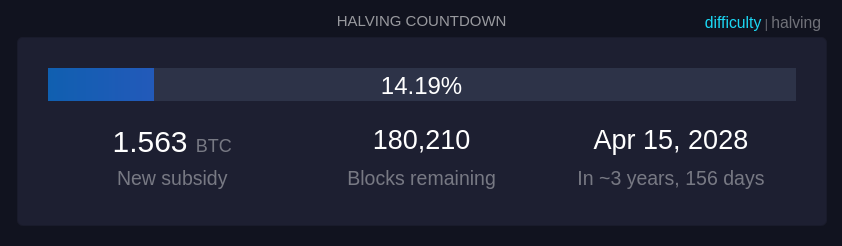 Quanto tempo demora até o próximo halving, um evento no Bitcoin que ocorre aproximadamente a cada 210.000 blocos minerados, ou cerca de quatro anos. Durante o halving, a recompensa que os mineradores recebem por adicionar um novo bloco à blockchain é reduzida pela metade. --- 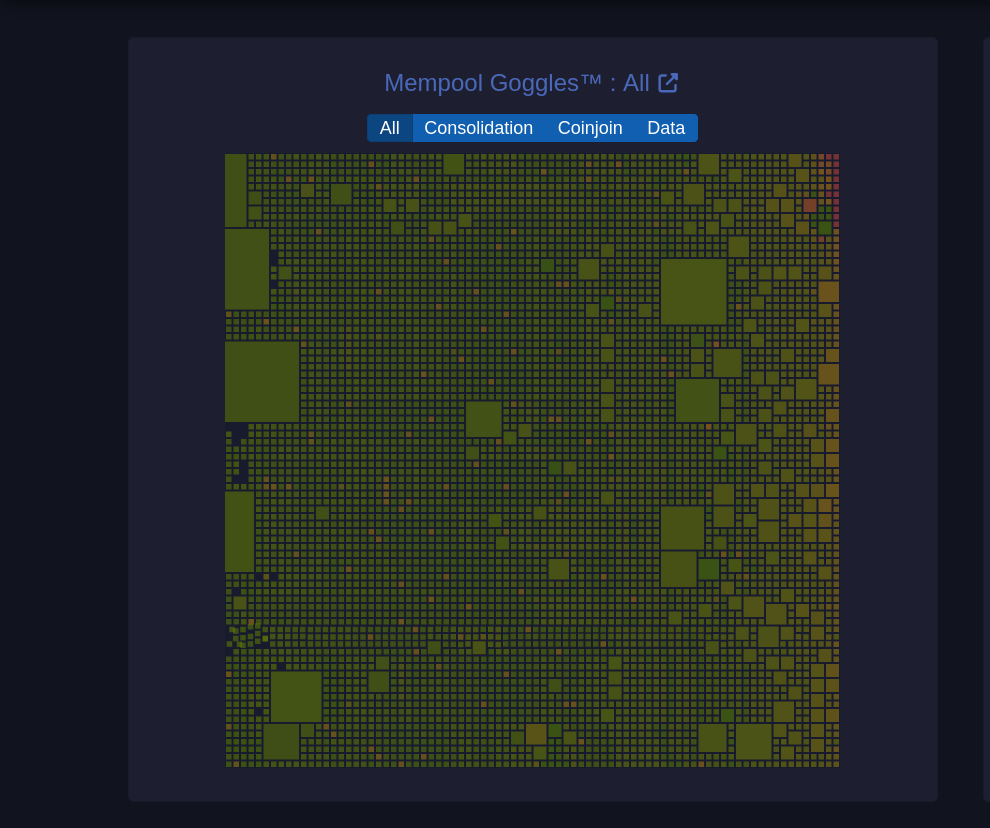 Um diagrama visual da mempool que mostra o estado das transações pendentes na rede. #### Tamanhos de blocos O tamanho de cada quadrado representa o tamanho da transação em bytes. **Filtros (Consolidação, Coinjoin, Dados):** Permite visualizar categorias específicas de transações: * **Consolidação**: Transações de consolidação agrupam pequenos UTXOs em um único UTXO maior para simplificar e baratear futuras transações. (UTXOs merecem um artigo dedicado) * **Coinjoin**: Transações CoinJoin são usadas para melhorar a privacidade, misturando transações de vários usuários em uma única transação. * **Dados**: Mostra transações que contêm dados adicionais, que podem incluir informações não financeiras, como mensagens. --- 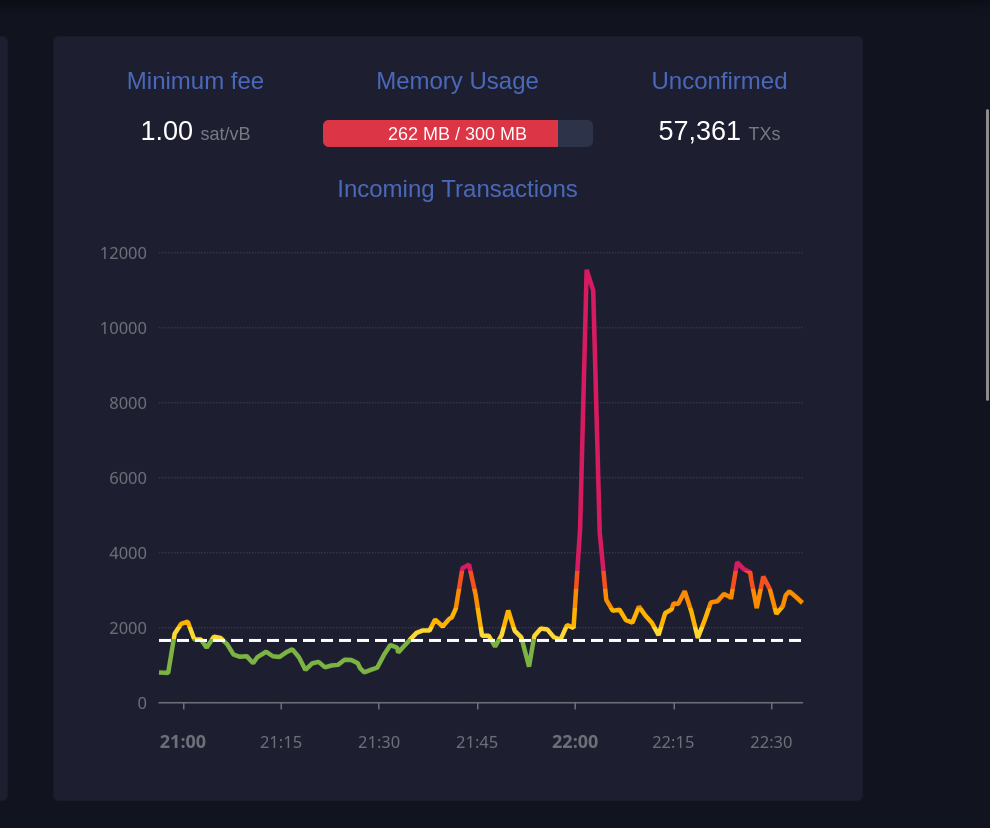 Este gráfico exibe o número de transações recebidas ao longo do tempo. #### Taxa mínima (1 sat/vB): Indica a taxa mínima atualmente aceita pela mempool. Se a mempool estiver cheia, transações que paguem menos do que a taxa mínima podem ser excluídas para dar lugar a transações de maior prioridade. #### Uso de memória (259 MB / 300 MB): A mempool tem um limite de memória. Quando está cheia, transações de taxa mais baixa podem ser descartadas para abrir espaço para aquelas com taxas mais altas, priorizando-as para inclusão em blocos. #### Transações não confirmadas (59.361): Indica o número total de transações pendentes que aguardam confirmação. Quanto maior o número de transações na mempool, maior a probabilidade de que as taxas aumentem para garantir uma confirmação mais rápida. ---  Essa seção mostra transações que foram substituídas utilizando o mecanismo RBF (Replace-By-Fee), que permite substituir uma transação com uma taxa mais alta para acelerar sua confirmação. #### TXID Este é o identificador da transação (Transaction ID), exibido parcialmente para abreviar o espaço. Cada transação tem um identificador único na blockchain. #### Previous fee Exibe a taxa de transação original paga na primeira tentativa, medida em satoshis por vByte (sat/vB). Esta taxa inicial provavelmente era baixa demais, resultando em uma demora na confirmação. #### New fee Mostra a nova taxa de transação, também em satoshis por vByte, definida para substituir a taxa anterior. Uma taxa maior aumenta as chances de inclusão rápida em um bloco. #### Status (RBF) RBF indica que a transação foi substituída utilizando o recurso "Replace-By-Fee". Isso significa que a nova transação cancelou e substituiu a original, e o minerador escolherá a transação com a taxa mais alta para incluir no próximo bloco. --- 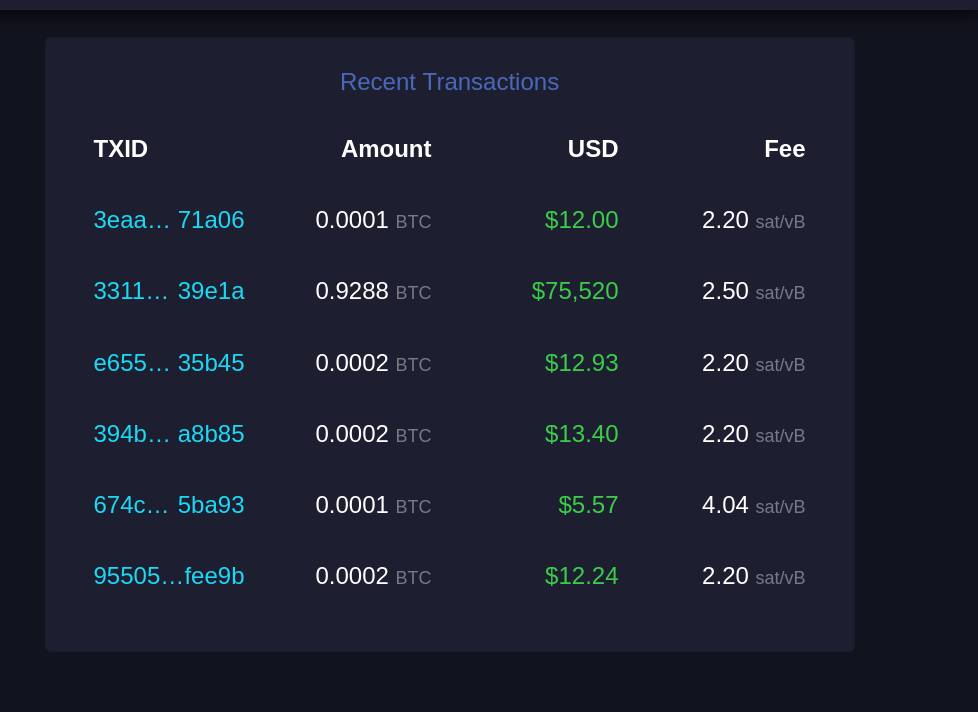 Esta seção lista transações recentes que entraram na mempool e aguardam confirmação. #### TXID Similar ao "Recent Replacements", este é o identificador único da transação. #### Amount Exibe a quantidade de Bitcoin transferida nessa transação, geralmente em frações de BTC (como 0.0001 BTC). Esta é a quantia enviada pelo remetente ao destinatário. #### USD Mostra o valor da transação em dólares americanos (USD), calculado com base na taxa de câmbio atual. Serve para dar uma ideia de quanto a transação representa em moeda fiduciária. #### Fee Exibe a taxa de transação paga, em satoshis por vByte (sat/vB). Uma taxa mais alta em relação à média aumenta a probabilidade de confirmação mais rápida, pois as transações com taxas mais elevadas são priorizadas pelos mineradores. --- E acabou. Espero que isso tenha sido útil para você e tenha agregado mais entendimento sobre esse complexo e maravilhoso mundo do Bitcoin. Se foi, considere compartilhar com alguém que precise. E se tem sugestões de melhoria, por favor, não deixe de comentar, o conhecimento está dispero na sociedade. Por fim, stay humble and stack sats! @ ec09d831:42c80ce4
2024-11-11 22:18:22-*Doğru diye bir şey yoktur.* -**Peki bu doğru mu?** -*Gerçek bilinemez.* -**Nereden biliyorsun?** -*Kesinlik yoktur.* -**Kesinlikle mi?** -*Sadece beş duyunuz gerçek bilgiyi sağlar.* -**Beş duyudan hangisi bu kanıya vardı?** -*Mantıksal argümanlar KANIT değildir.* -**Bunun için kanıtınız nedir?** -*Sadece fiziksel âlem gerçektir.* -**Bu savın kendisi bile fiziksel âlemde geliştirilmiş değildir, dolayısıyla kendi kendini çürütür.**
@ ec09d831:42c80ce4
2024-11-11 22:18:22-*Doğru diye bir şey yoktur.* -**Peki bu doğru mu?** -*Gerçek bilinemez.* -**Nereden biliyorsun?** -*Kesinlik yoktur.* -**Kesinlikle mi?** -*Sadece beş duyunuz gerçek bilgiyi sağlar.* -**Beş duyudan hangisi bu kanıya vardı?** -*Mantıksal argümanlar KANIT değildir.* -**Bunun için kanıtınız nedir?** -*Sadece fiziksel âlem gerçektir.* -**Bu savın kendisi bile fiziksel âlemde geliştirilmiş değildir, dolayısıyla kendi kendini çürütür.** @ f462d21e:1390b6b1
2024-11-10 11:44:59eyJfaWQiOiIxMGRmODZiMS02NTdjLTQwNjUtYjVjOC1kNmY2YmJlNjRhN2IiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwidXNlcm5hbWUiOiJqb2UiLCJhZFR5cGUiOiJPTkxJTkVfU0VMTCIsImNvdW50cnkiOiJVbml0ZWQgS2luZ2RvbSIsImNvdW50cnlDb2RlIjoiR0IiLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6IlZFTk1PIiwicHJpY2VJbnB1dFR5cGUiOiJNQVJLRVQiLCJtYXJnaW4iOjMsImZpeGVkUHJpY2UiOjAsIm1pbkFtb3VudCI6MCwibWF4QW1vdW50IjowLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCByYXRlcyByZWFsbHkiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDFUMDc6MTk6MjEuMDk5WiIsIm1hcmtldFByaWNlIjoxNjUuMzF9
@ f462d21e:1390b6b1
2024-11-10 11:44:59eyJfaWQiOiIxMGRmODZiMS02NTdjLTQwNjUtYjVjOC1kNmY2YmJlNjRhN2IiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwidXNlcm5hbWUiOiJqb2UiLCJhZFR5cGUiOiJPTkxJTkVfU0VMTCIsImNvdW50cnkiOiJVbml0ZWQgS2luZ2RvbSIsImNvdW50cnlDb2RlIjoiR0IiLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6IlZFTk1PIiwicHJpY2VJbnB1dFR5cGUiOiJNQVJLRVQiLCJtYXJnaW4iOjMsImZpeGVkUHJpY2UiOjAsIm1pbkFtb3VudCI6MCwibWF4QW1vdW50IjowLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCByYXRlcyByZWFsbHkiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDFUMDc6MTk6MjEuMDk5WiIsIm1hcmtldFByaWNlIjoxNjUuMzF9 @ a10260a2:caa23e3e
2024-11-10 04:35:34nostr:npub1nkmta4dmsa7pj25762qxa6yqxvrhzn7ug0gz5frp9g7p3jdscnhsu049fn added support for [classified listings (NIP-99)](https://github.com/sovbiz/Cypher-Nostr-Edition/commit/cd3bf585c77a85421de031db1d8ebd3911ba670d) about a month ago and recently announced this update that allows for creating/editing listings and blog posts via the dashboard. In other words, listings created on the website are also able to be viewed and edited on other Nostr apps like Amethyst and Shopstr. Interoperability FTW. I took some screenshots to give you an idea of how things work. The [home page](https://cypher.space/) is clean with the ability to search for profiles by name, npub, or Nostr address (NIP-05). 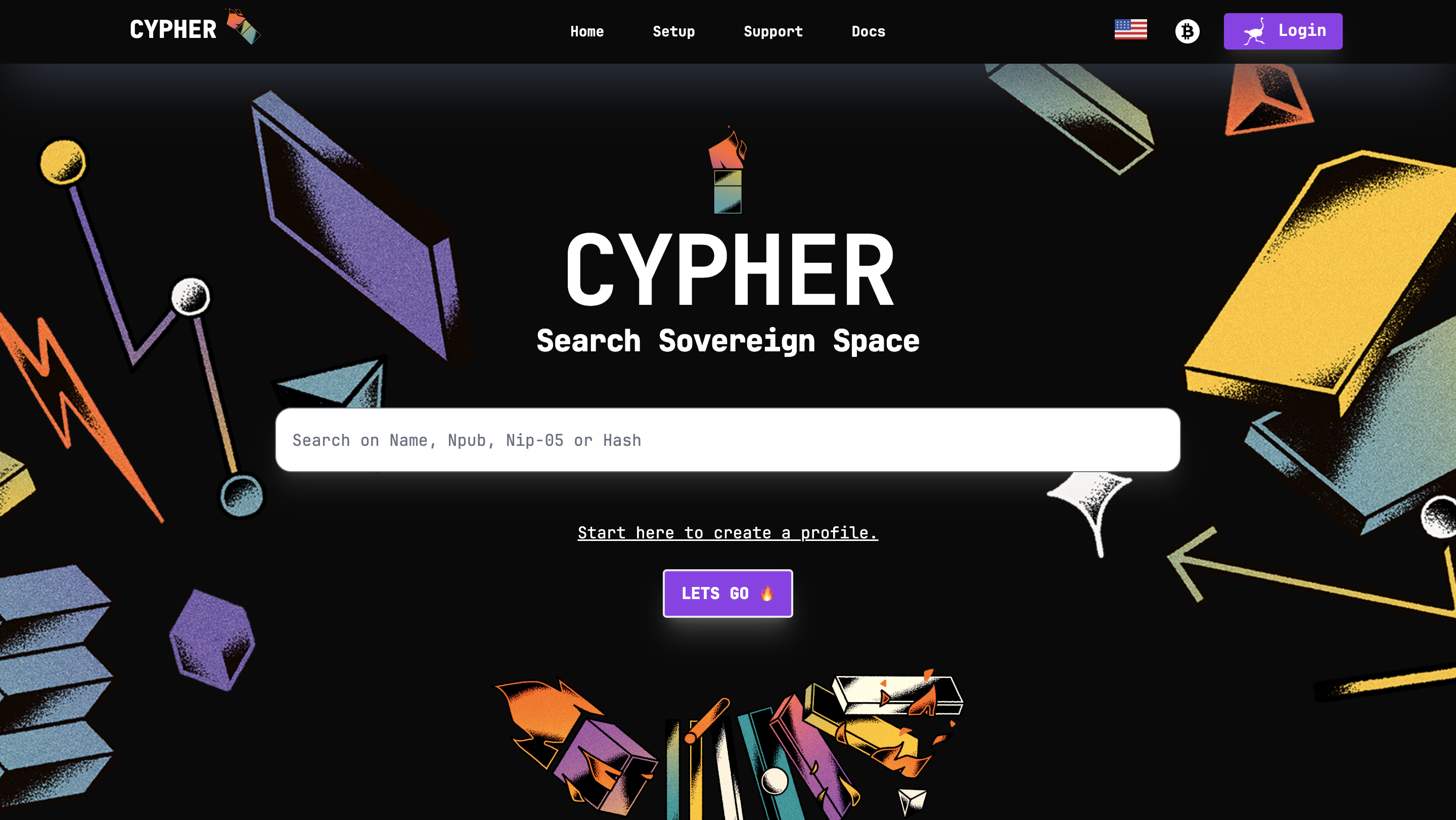 Clicking login allows signing in with a browser extension. 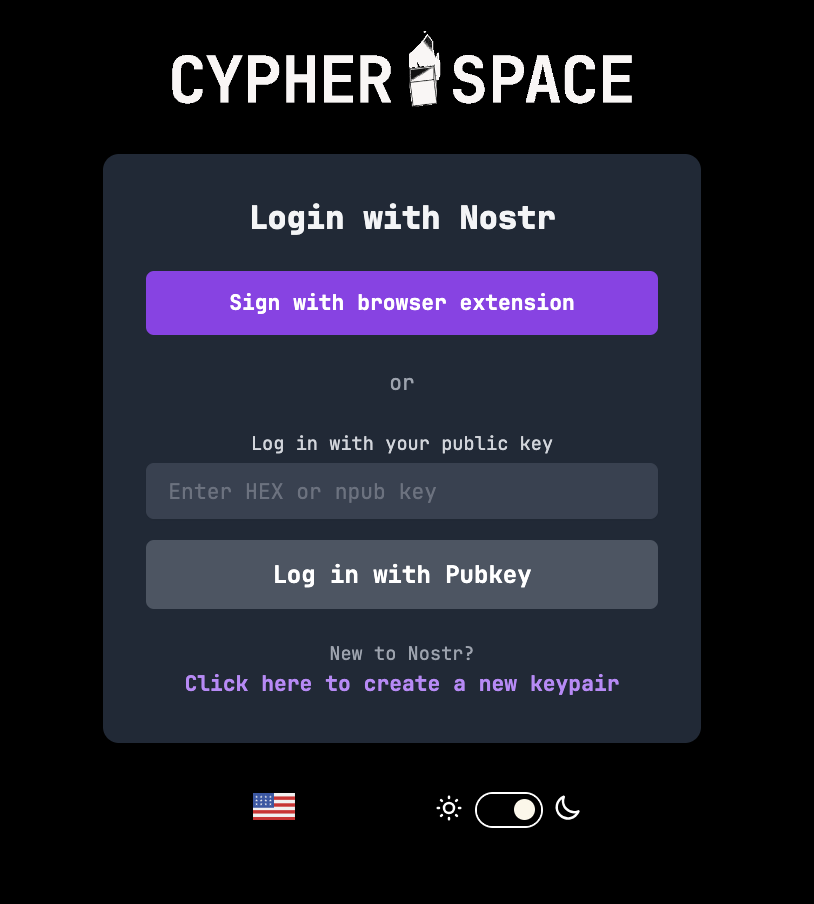 The dashboard gives an overview of the amount of notes posted (both short and long form) and products listed. 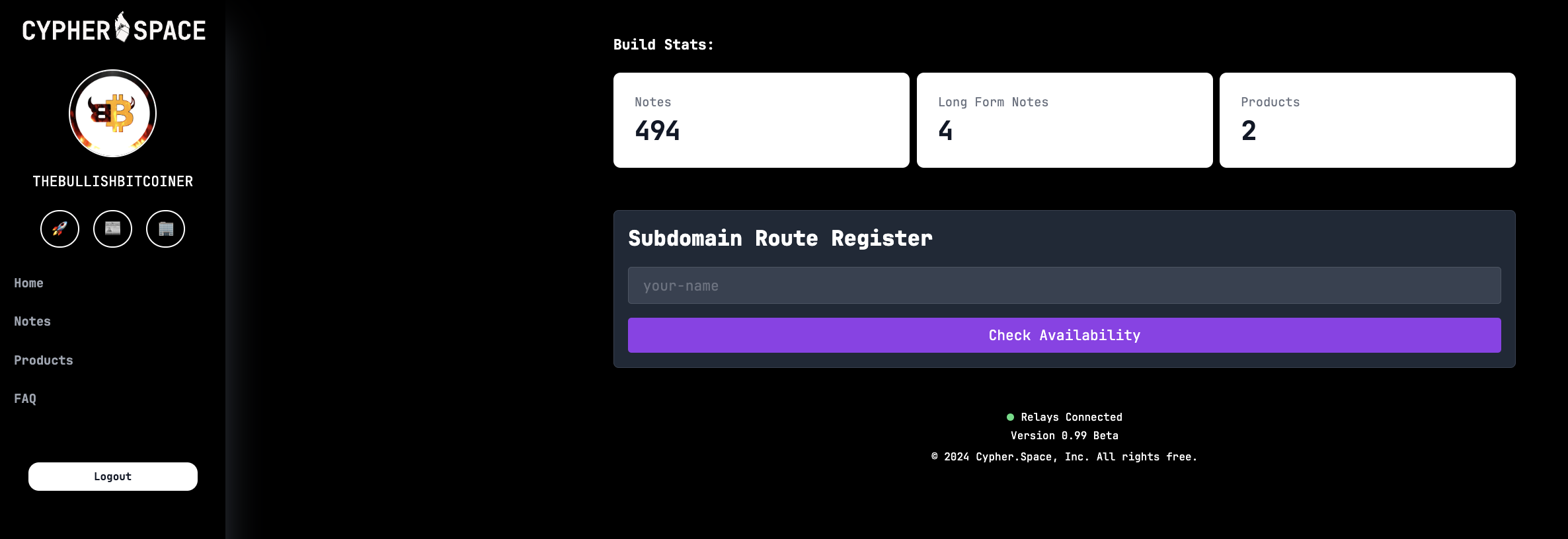 Existing blog posts (i.e. long form notes) are synced. 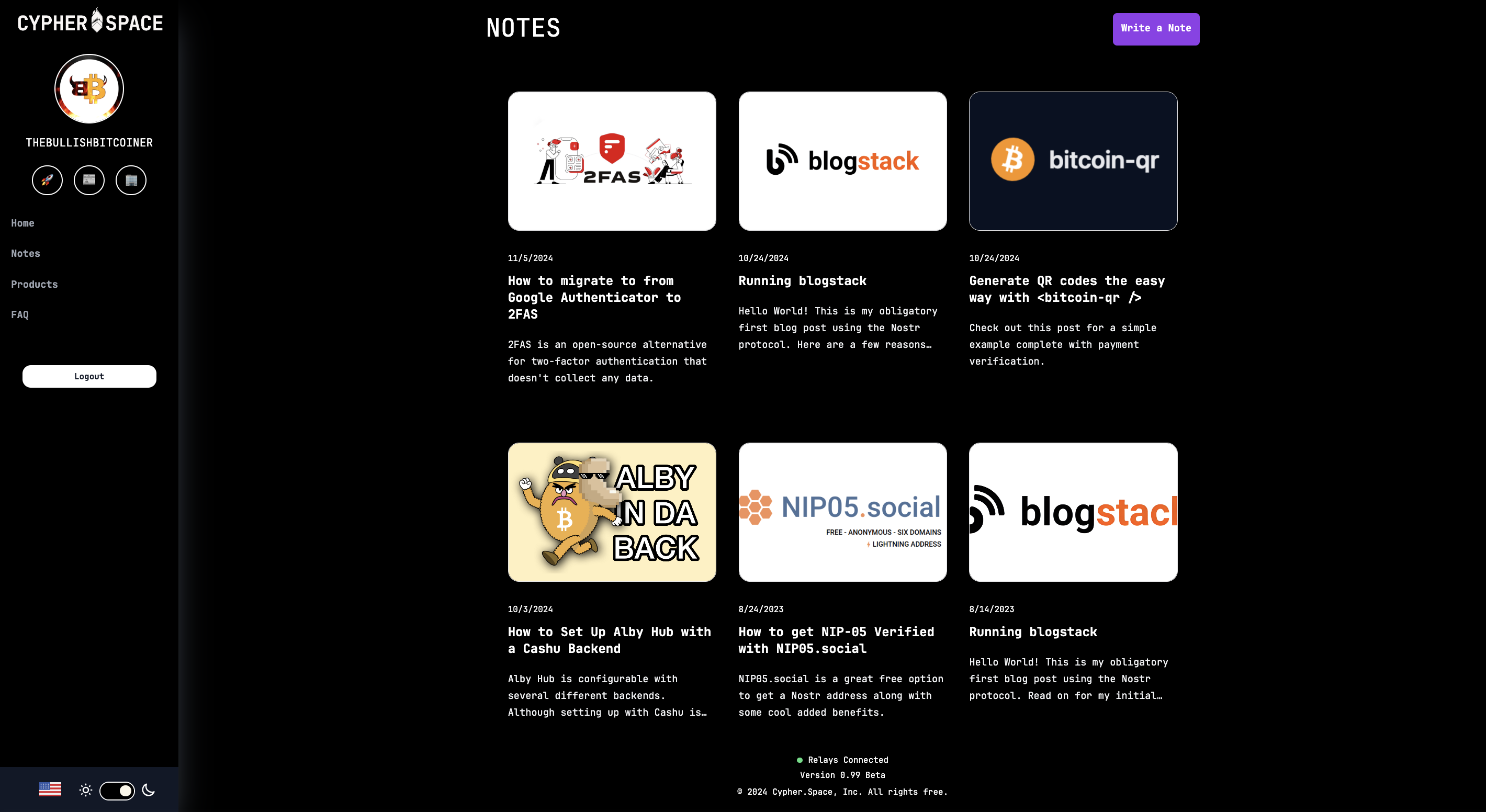 Same for product listings. There’s a nice interface to create new ones and preview them before publishing. 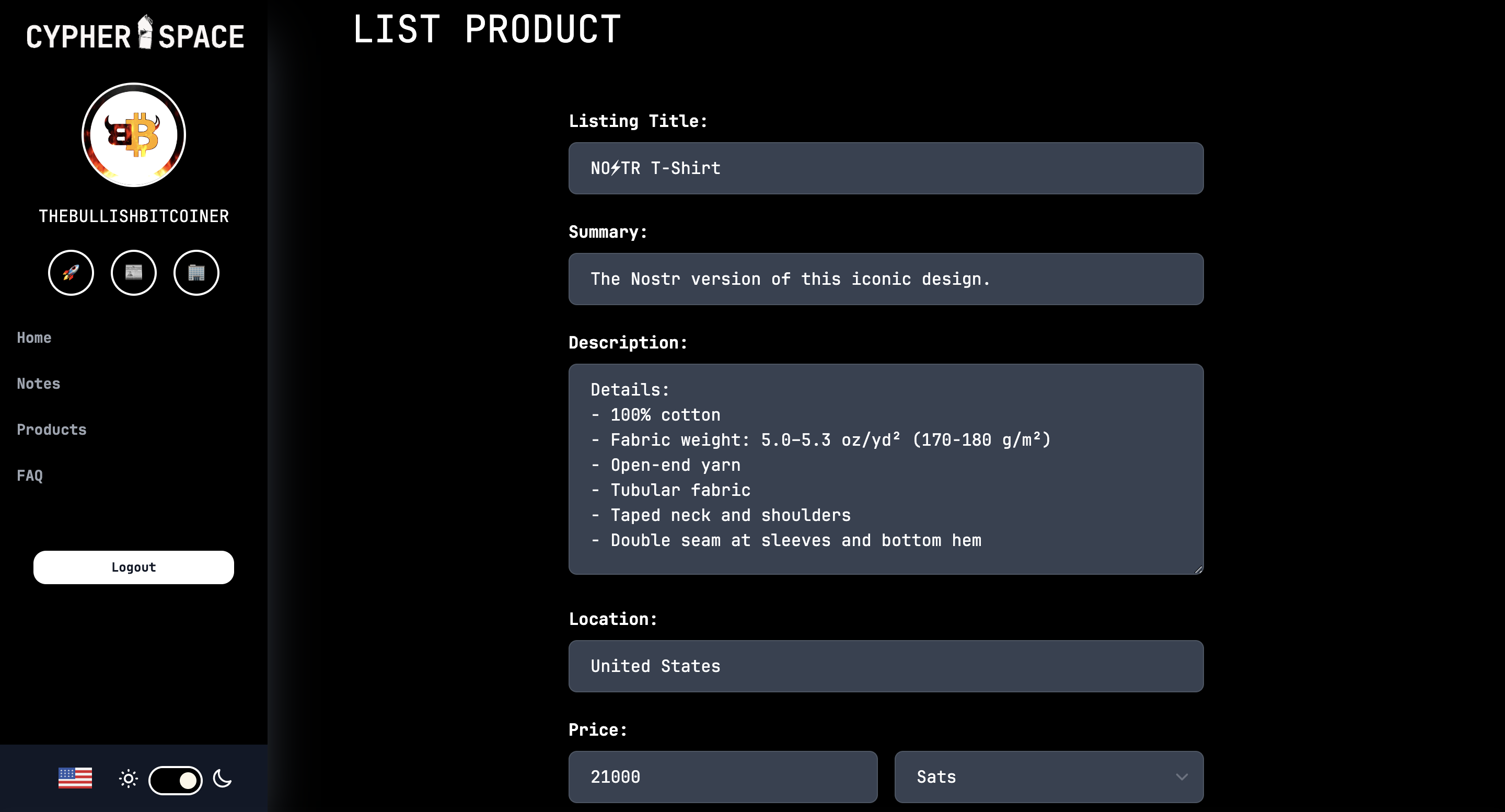 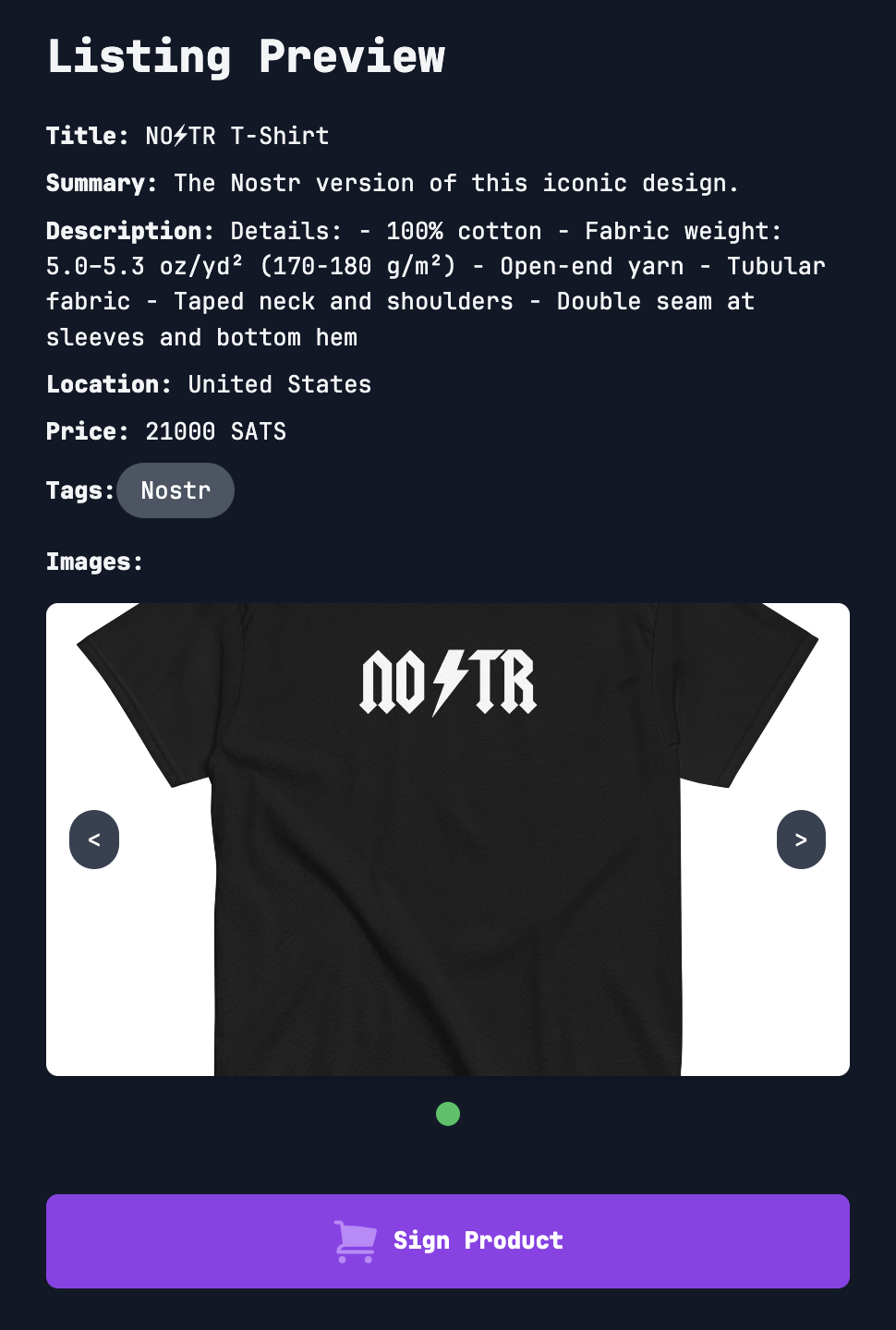 That’s all for now. As you can see, super slick stuff! Bullish on Cypher. So much so I had to support the project and buy a subdomain. 😎 https://bullish.cypher.space originally posted at https://stacker.news/items/760592
@ a10260a2:caa23e3e
2024-11-10 04:35:34nostr:npub1nkmta4dmsa7pj25762qxa6yqxvrhzn7ug0gz5frp9g7p3jdscnhsu049fn added support for [classified listings (NIP-99)](https://github.com/sovbiz/Cypher-Nostr-Edition/commit/cd3bf585c77a85421de031db1d8ebd3911ba670d) about a month ago and recently announced this update that allows for creating/editing listings and blog posts via the dashboard. In other words, listings created on the website are also able to be viewed and edited on other Nostr apps like Amethyst and Shopstr. Interoperability FTW. I took some screenshots to give you an idea of how things work. The [home page](https://cypher.space/) is clean with the ability to search for profiles by name, npub, or Nostr address (NIP-05). 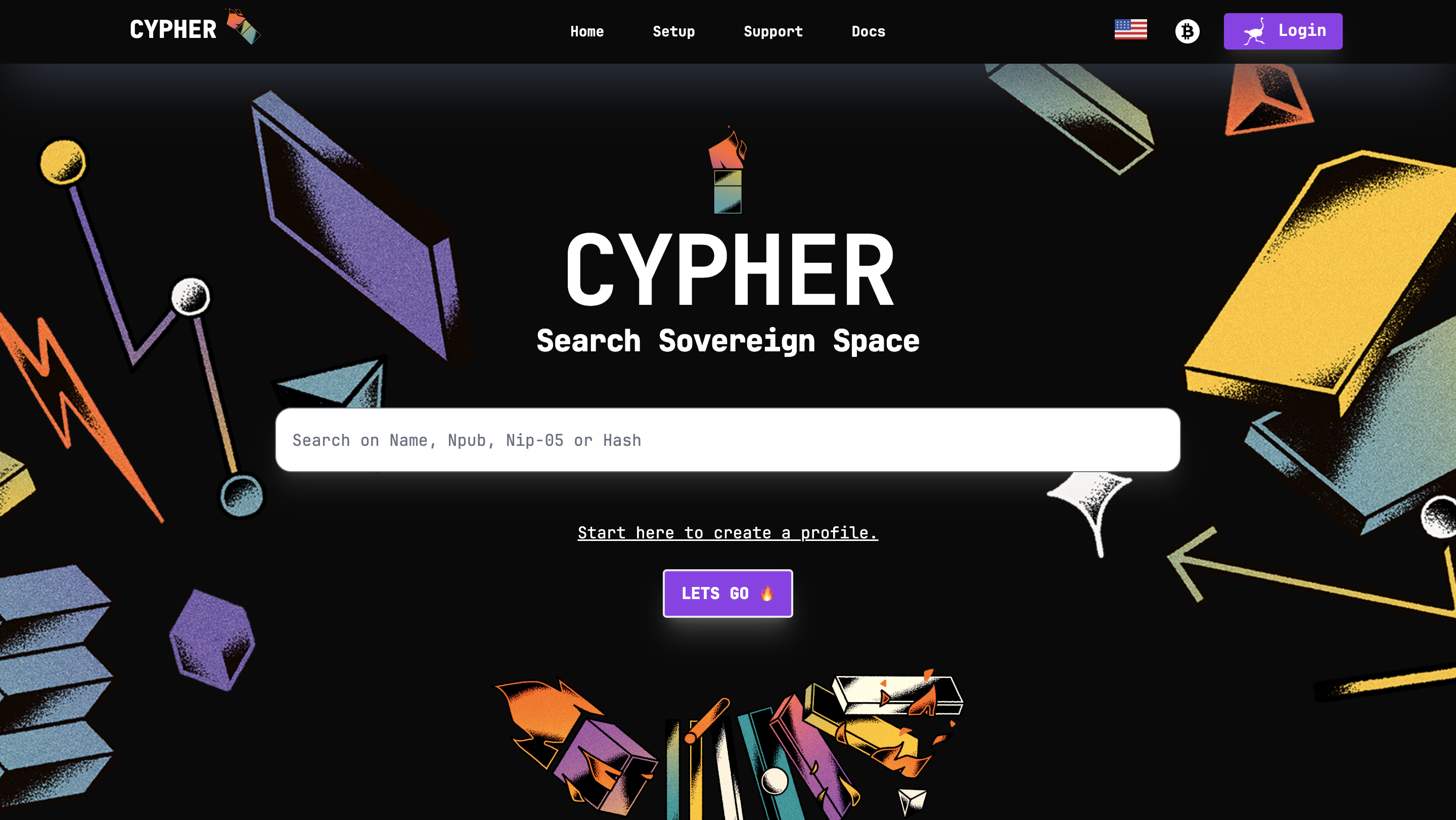 Clicking login allows signing in with a browser extension. 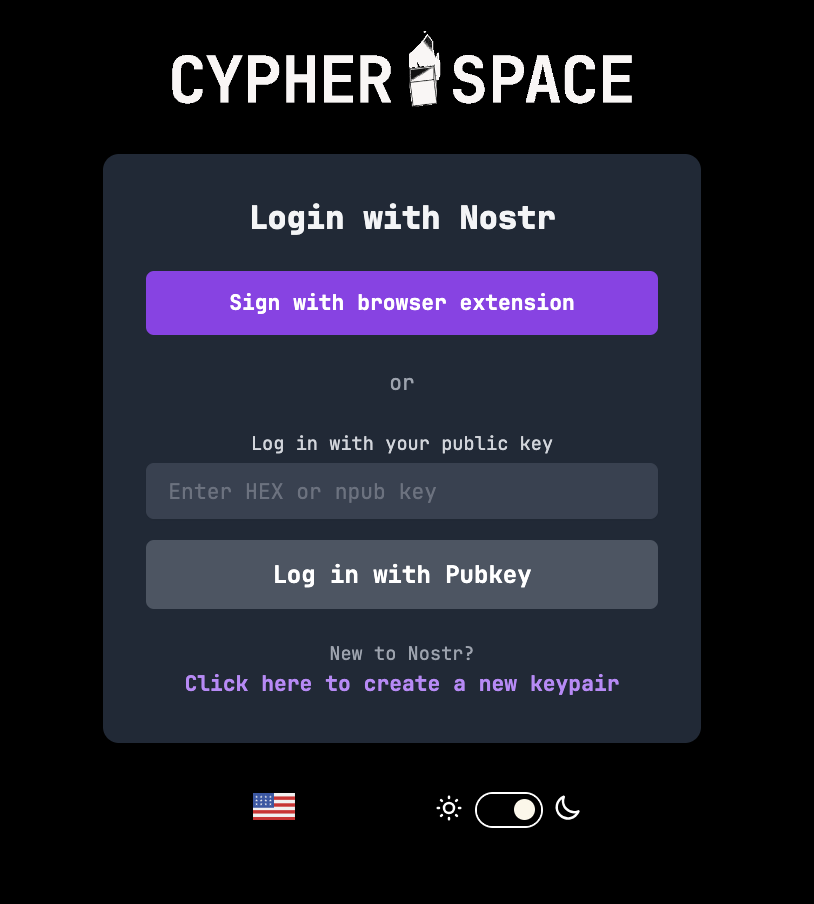 The dashboard gives an overview of the amount of notes posted (both short and long form) and products listed. 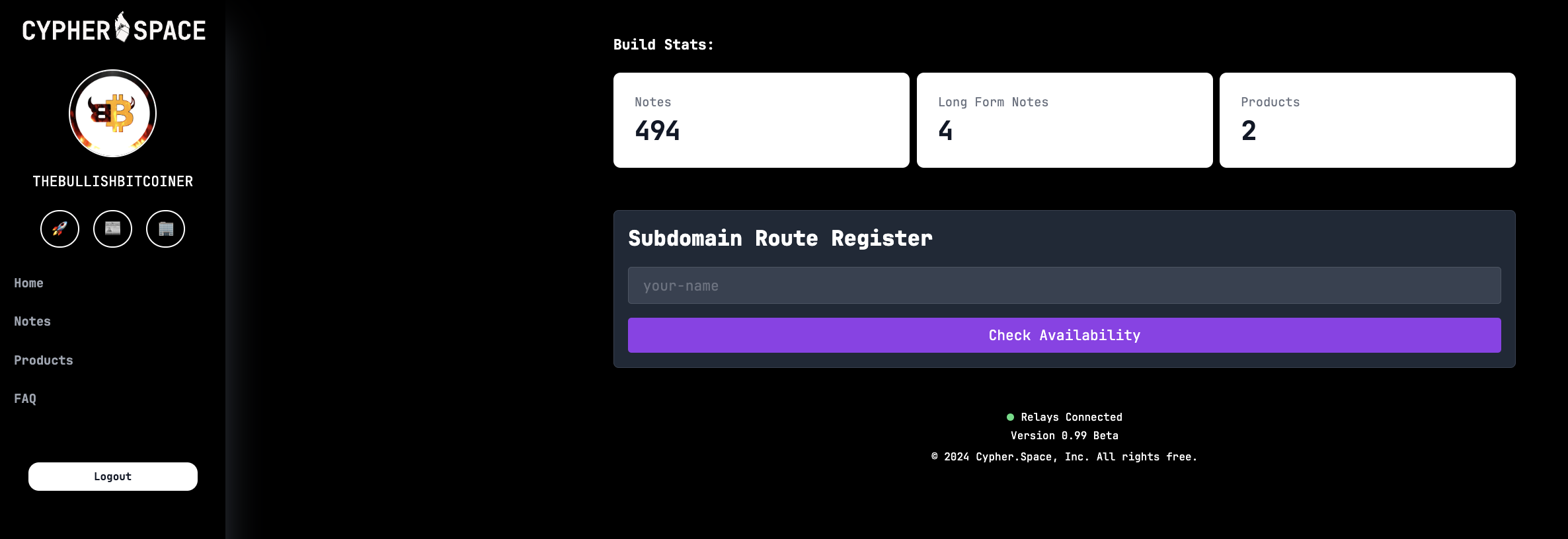 Existing blog posts (i.e. long form notes) are synced. 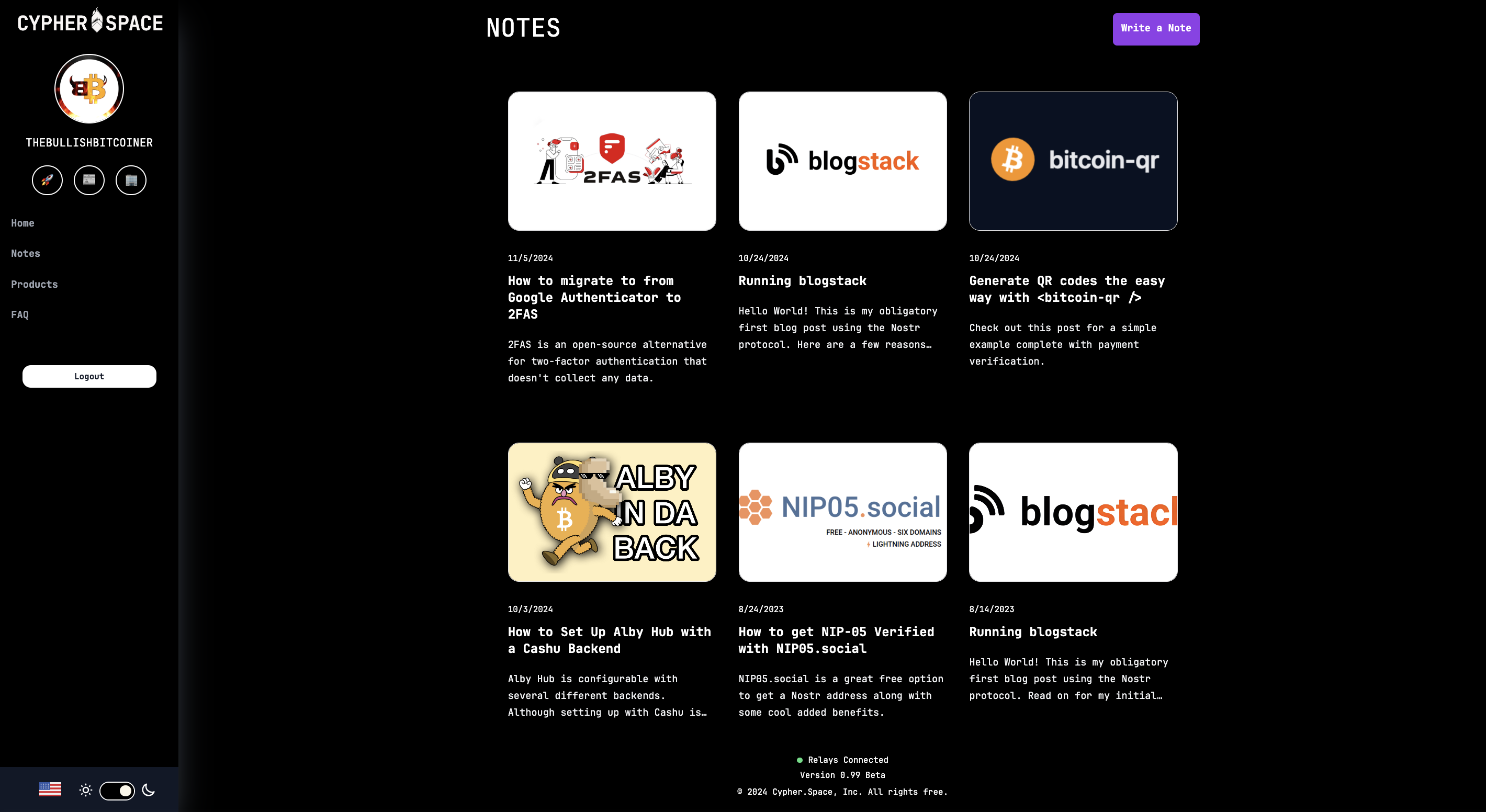 Same for product listings. There’s a nice interface to create new ones and preview them before publishing. 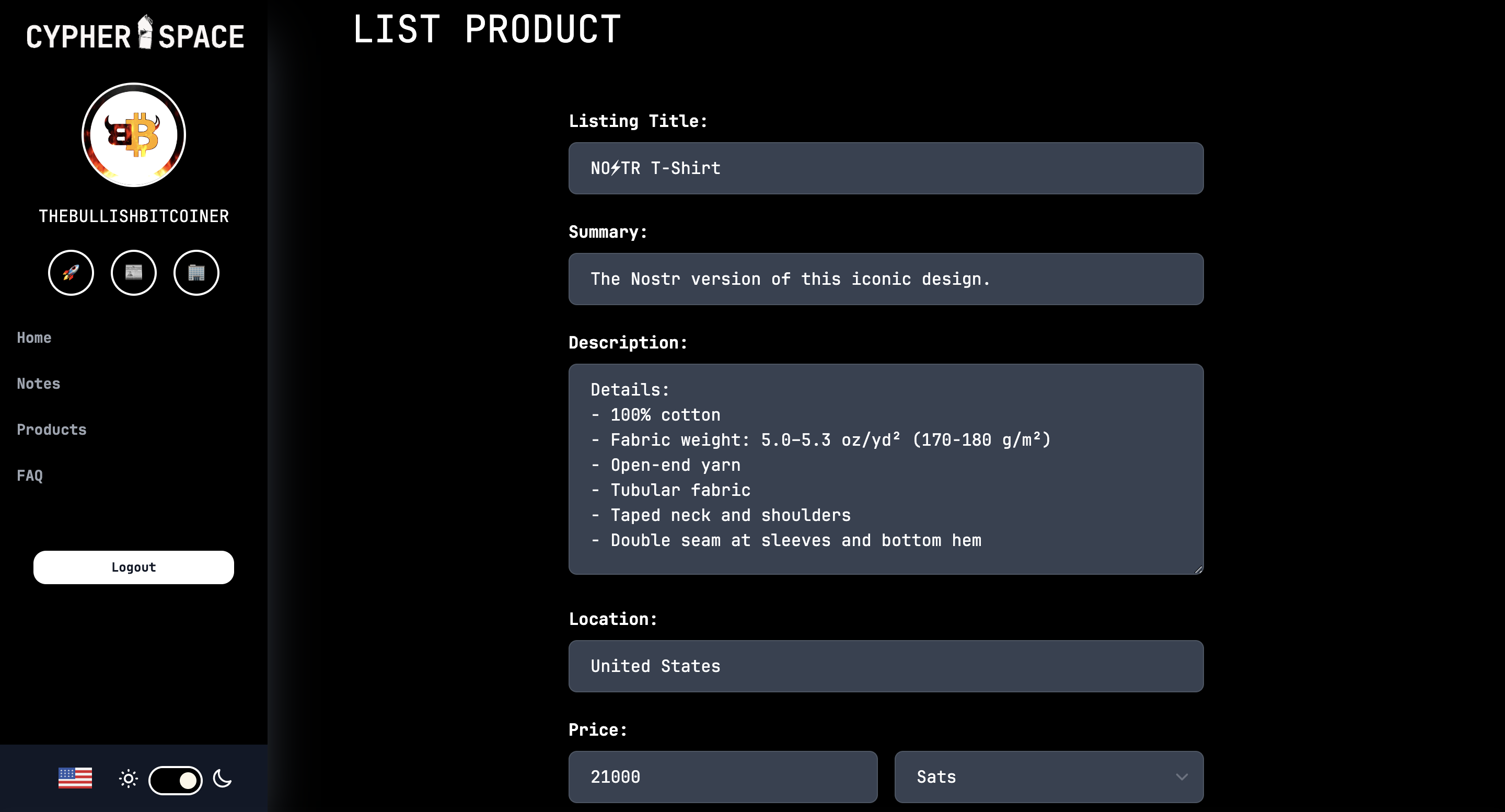 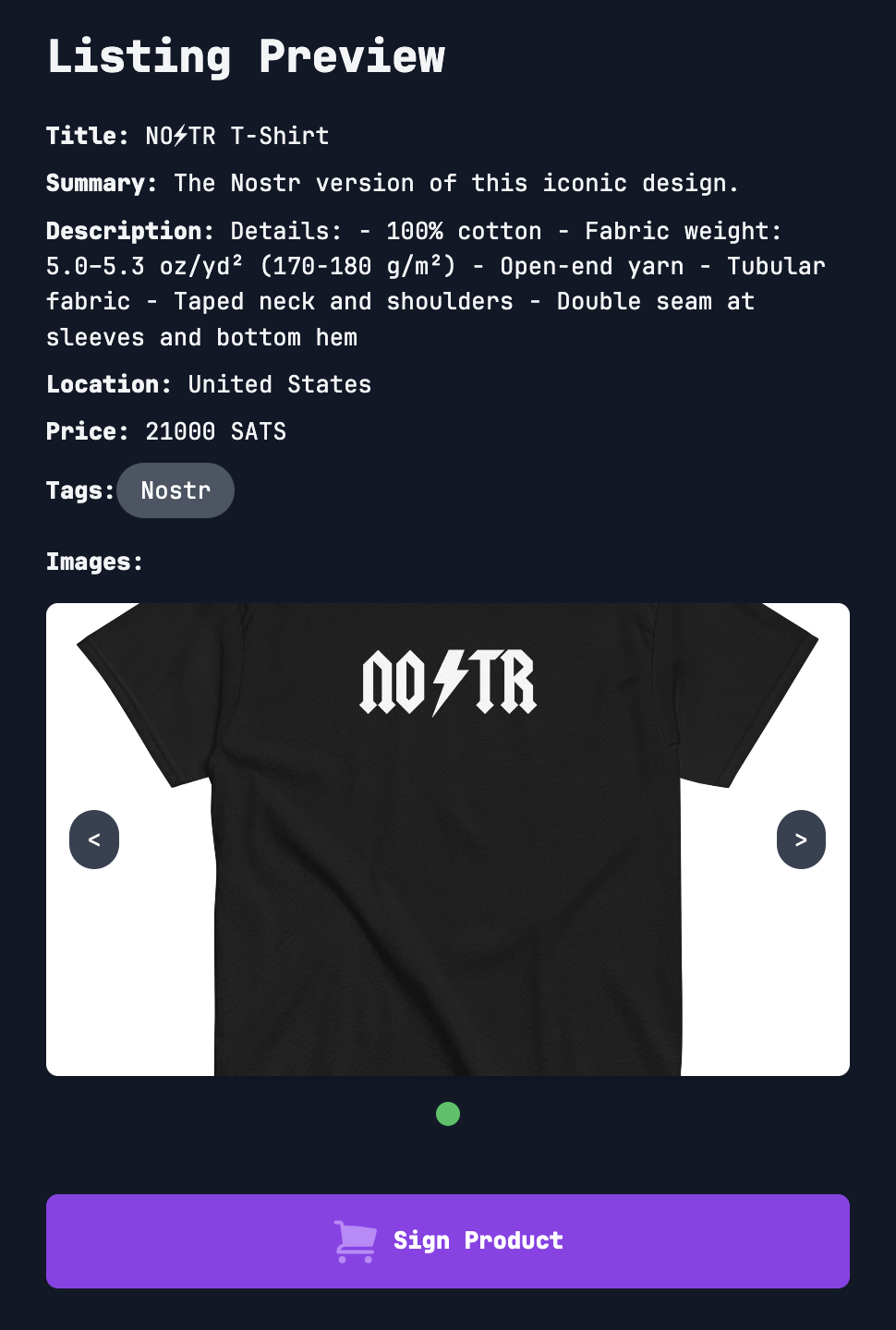 That’s all for now. As you can see, super slick stuff! Bullish on Cypher. So much so I had to support the project and buy a subdomain. 😎 https://bullish.cypher.space originally posted at https://stacker.news/items/760592 @ b34f99f1:006b0fcc
2024-11-09 17:03:35eyJfaWQiOiI5NDEyN2JmZi00ZDhlLTRmODUtOThiMy1kNGRhNDNhMTgxODQiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiTkFUSU9OQUxfQkFOSyIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjozLCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjEwMCwibWF4QW1vdW50IjowLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCByYXRlcyBqdXN0IGZvciB5b3UiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMTQ6Mzk6MjMuNzU5WiIsIm1hcmtldFByaWNlIjoxNjMuOX0=
@ b34f99f1:006b0fcc
2024-11-09 17:03:35eyJfaWQiOiI5NDEyN2JmZi00ZDhlLTRmODUtOThiMy1kNGRhNDNhMTgxODQiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiTkFUSU9OQUxfQkFOSyIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjozLCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjEwMCwibWF4QW1vdW50IjowLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCByYXRlcyBqdXN0IGZvciB5b3UiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMTQ6Mzk6MjMuNzU5WiIsIm1hcmtldFByaWNlIjoxNjMuOX0= @ b34f99f1:006b0fcc
2024-11-09 17:03:02deleted
@ b34f99f1:006b0fcc
2024-11-09 17:03:02deleted @ b34f99f1:006b0fcc
2024-11-09 17:02:11eyJfaWQiOiI0NTljZTMxMC1mNDlkLTQ2NDAtYTNmZi0xODVjYTZiOGU3MDMiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiTE9DQUxfQlVZIiwiY291bnRyeSI6IlVuaXRlZCBTdGF0ZXMgb2YgQW1lcmljYSIsImNvdW50cnlDb2RlIjoiVVMiLCJsYXQiOjI3Ljk0Nzc2LCJsb24iOi04Mi40NTg0NDQsImdlY29kZSI6eyJwbGFjZV9pZCI6MjcwMDI2NzQ0LCJsaWNlbmNlIjoiRGF0YSDCqSBPcGVuU3RyZWV0TWFwIGNvbnRyaWJ1dG9ycywgT0RiTCAxLjAuIGh0dHBzOi8vb3NtLm9yZy9jb3B5cmlnaHQiLCJvc21fdHlwZSI6InJlbGF0aW9uIiwib3NtX2lkIjoxMjMyMTE1NiwibGF0IjoiMjcuOTQ3OTIiLCJsb24iOiItODIuNDU4MTIxMDYzNjExOTciLCJkaXNwbGF5X25hbWUiOiJSaXZlcnNpZGUsIFRhbXBhLCBIaWxsc2Jvcm91Z2ggQ291bnR5LCBGbG9yaWRhLCBVbml0ZWQgU3RhdGVzIiwiYWRkcmVzcyI6eyJoYW1sZXQiOiJSaXZlcnNpZGUiLCJjaXR5IjoiVGFtcGEiLCJjb3VudHkiOiJIaWxsc2Jvcm91Z2ggQ291bnR5Iiwic3RhdGUiOiJGbG9yaWRhIiwiSVNPMzE2Ni0yLWx2bDQiOiJVUy1GTCIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIiwiY291bnRyeV9jb2RlIjoidXMifSwiYm91bmRpbmdib3giOlsiMjcuOTQ3NDg2MiIsIjI3Ljk0ODM2NDEiLCItODIuNDU4OTg5MSIsIi04Mi40NTgwMDUzIl19LCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MTAsImZpeGVkUHJpY2UiOjAsImJ1eWVyU2V0dGxlbWVudEFkZHJlc3MiOiIiLCJtaW5BbW91bnQiOjUwMDAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwibXNnIjoid2FpdCBmb3IgbWUgYXQgYnVzIHN0YXRpb24iLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMjA6NDU6MTYuNjgxWiIsIm1hcmtldFByaWNlIjoxNjUuNH0=
@ b34f99f1:006b0fcc
2024-11-09 17:02:11eyJfaWQiOiI0NTljZTMxMC1mNDlkLTQ2NDAtYTNmZi0xODVjYTZiOGU3MDMiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiTE9DQUxfQlVZIiwiY291bnRyeSI6IlVuaXRlZCBTdGF0ZXMgb2YgQW1lcmljYSIsImNvdW50cnlDb2RlIjoiVVMiLCJsYXQiOjI3Ljk0Nzc2LCJsb24iOi04Mi40NTg0NDQsImdlY29kZSI6eyJwbGFjZV9pZCI6MjcwMDI2NzQ0LCJsaWNlbmNlIjoiRGF0YSDCqSBPcGVuU3RyZWV0TWFwIGNvbnRyaWJ1dG9ycywgT0RiTCAxLjAuIGh0dHBzOi8vb3NtLm9yZy9jb3B5cmlnaHQiLCJvc21fdHlwZSI6InJlbGF0aW9uIiwib3NtX2lkIjoxMjMyMTE1NiwibGF0IjoiMjcuOTQ3OTIiLCJsb24iOiItODIuNDU4MTIxMDYzNjExOTciLCJkaXNwbGF5X25hbWUiOiJSaXZlcnNpZGUsIFRhbXBhLCBIaWxsc2Jvcm91Z2ggQ291bnR5LCBGbG9yaWRhLCBVbml0ZWQgU3RhdGVzIiwiYWRkcmVzcyI6eyJoYW1sZXQiOiJSaXZlcnNpZGUiLCJjaXR5IjoiVGFtcGEiLCJjb3VudHkiOiJIaWxsc2Jvcm91Z2ggQ291bnR5Iiwic3RhdGUiOiJGbG9yaWRhIiwiSVNPMzE2Ni0yLWx2bDQiOiJVUy1GTCIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIiwiY291bnRyeV9jb2RlIjoidXMifSwiYm91bmRpbmdib3giOlsiMjcuOTQ3NDg2MiIsIjI3Ljk0ODM2NDEiLCItODIuNDU4OTg5MSIsIi04Mi40NTgwMDUzIl19LCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MTAsImZpeGVkUHJpY2UiOjAsImJ1eWVyU2V0dGxlbWVudEFkZHJlc3MiOiIiLCJtaW5BbW91bnQiOjUwMDAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwibXNnIjoid2FpdCBmb3IgbWUgYXQgYnVzIHN0YXRpb24iLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMjA6NDU6MTYuNjgxWiIsIm1hcmtldFByaWNlIjoxNjUuNH0= @ bcea2b98:7ccef3c9
2024-11-09 17:01:32Weekends are the perfect time to unwind, explore, or spend time doing what we love. How would you spend your ideal weekend? Would it be all about relaxation, or would you be out and about? For me, an ideal weekend would start with a slow Saturday morning, a good book and coffee. Then I would spend the afternoon exploring local trails and looking for snacks. Then always a slow Sunday night hopefully. originally posted at https://stacker.news/items/760492
@ bcea2b98:7ccef3c9
2024-11-09 17:01:32Weekends are the perfect time to unwind, explore, or spend time doing what we love. How would you spend your ideal weekend? Would it be all about relaxation, or would you be out and about? For me, an ideal weekend would start with a slow Saturday morning, a good book and coffee. Then I would spend the afternoon exploring local trails and looking for snacks. Then always a slow Sunday night hopefully. originally posted at https://stacker.news/items/760492 @ b34f99f1:006b0fcc
2024-11-09 16:35:11eyJfaWQiOiI0NzgyYTkzNC02ZTUzLTRlYTctOWUwOC04YTAwZjJmNGQ4NTAiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiQ1JZUFRPQ1VSUkVOQ1kiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJmaXhlZFByaWNlIjoxOTAsIm1pbkFtb3VudCI6MjAwLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiJsdGMgfCBidGMiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMTQ6NDA6MjYuODk0WiJ9
@ b34f99f1:006b0fcc
2024-11-09 16:35:11eyJfaWQiOiI0NzgyYTkzNC02ZTUzLTRlYTctOWUwOC04YTAwZjJmNGQ4NTAiLCJwdWJsaWNLZXkiOiJiMzRmOTlmMTEwYmI2NWZmNGI1NTI3ZjhmYjFkMDE1OTUxYTMwMzgzNzBmZDk1YWRjMzRkODFkOTAwNmIwZmNjIiwidXNlcm5hbWUiOiJsaWFtIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiQ1JZUFRPQ1VSUkVOQ1kiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJmaXhlZFByaWNlIjoxOTAsIm1pbkFtb3VudCI6MjAwLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiJsdGMgfCBidGMiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMTQ6NDA6MjYuODk0WiJ9 @ 1eb966a6:e3eddf94
2024-11-09 13:19:43eyJfaWQiOiJhNThkNzNlMi05NzAwLTQ3ZmUtODZiMy0xZGU0NWQwZGRhZDIiLCJwdWJsaWNLZXkiOiIxZWI5NjZhNmEwMjE4YWJhNTIwYWFhYzkzYmU3ZGQ4YmYzODMwZmM3NzEwYmM4MGNhZWEzYTZhNWUzZWRkZjk0IiwidXNlcm5hbWUiOiJoYW5rIiwiYWRUeXBlIjoiTE9DQUxfU0VMTCIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIG9mIEFtZXJpY2EiLCJjb3VudHJ5Q29kZSI6IlVTIiwibGF0IjozNC4wNTM2OTEsImxvbiI6LTExOC4yNDI3NjYsImdlY29kZSI6eyJwbGFjZV9pZCI6Mjg0ODczMDQ4LCJsaWNlbmNlIjoiRGF0YSDCqSBPcGVuU3RyZWV0TWFwIGNvbnRyaWJ1dG9ycywgT0RiTCAxLjAuIGh0dHBzOi8vb3NtLm9yZy9jb3B5cmlnaHQiLCJvc21fdHlwZSI6InJlbGF0aW9uIiwib3NtX2lkIjo2MzMzMTQ1LCJsYXQiOiIzNC4wNTM2OTYwNSIsImxvbiI6Ii0xMTguMjQyOTIxMjE4MzMzOTUiLCJkaXNwbGF5X25hbWUiOiJMb3MgQW5nZWxlcyBDaXR5IEhhbGwsIDIwMCwgTm9ydGggU3ByaW5nIFN0cmVldCwgQ2l2aWMgQ2VudGVyLCBEb3dudG93biwgTG9zIEFuZ2VsZXMsIExvcyBBbmdlbGVzIENvdW50eSwgQ2FsaWZvcm5pYSwgOTAwMTIsIFVuaXRlZCBTdGF0ZXMiLCJhZGRyZXNzIjp7ImJ1aWxkaW5nIjoiTG9zIEFuZ2VsZXMgQ2l0eSBIYWxsIiwiaG91c2VfbnVtYmVyIjoiMjAwIiwicm9hZCI6Ik5vcnRoIFNwcmluZyBTdHJlZXQiLCJxdWFydGVyIjoiQ2l2aWMgQ2VudGVyIiwic3VidXJiIjoiRG93bnRvd24iLCJjaXR5IjoiTG9zIEFuZ2VsZXMiLCJjb3VudHkiOiJMb3MgQW5nZWxlcyBDb3VudHkiLCJzdGF0ZSI6IkNhbGlmb3JuaWEiLCJJU08zMTY2LTItbHZsNCI6IlVTLUNBIiwicG9zdGNvZGUiOiI5MDAxMiIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIiwiY291bnRyeV9jb2RlIjoidXMifSwiYm91bmRpbmdib3giOlsiMzQuMDUzMDE0MSIsIjM0LjA1NDM3MTMiLCItMTE4LjI0MzUzIiwiLTExOC4yNDIwMDUyIl19LCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjowLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsIm1zZyI6Im1lZXQgbWUgb25seSBpbiBwdWJsaWMiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMDg6NTI6MjYuNzkzWiIsIm1hcmtldFByaWNlIjoxNjIuMTd9
@ 1eb966a6:e3eddf94
2024-11-09 13:19:43eyJfaWQiOiJhNThkNzNlMi05NzAwLTQ3ZmUtODZiMy0xZGU0NWQwZGRhZDIiLCJwdWJsaWNLZXkiOiIxZWI5NjZhNmEwMjE4YWJhNTIwYWFhYzkzYmU3ZGQ4YmYzODMwZmM3NzEwYmM4MGNhZWEzYTZhNWUzZWRkZjk0IiwidXNlcm5hbWUiOiJoYW5rIiwiYWRUeXBlIjoiTE9DQUxfU0VMTCIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIG9mIEFtZXJpY2EiLCJjb3VudHJ5Q29kZSI6IlVTIiwibGF0IjozNC4wNTM2OTEsImxvbiI6LTExOC4yNDI3NjYsImdlY29kZSI6eyJwbGFjZV9pZCI6Mjg0ODczMDQ4LCJsaWNlbmNlIjoiRGF0YSDCqSBPcGVuU3RyZWV0TWFwIGNvbnRyaWJ1dG9ycywgT0RiTCAxLjAuIGh0dHBzOi8vb3NtLm9yZy9jb3B5cmlnaHQiLCJvc21fdHlwZSI6InJlbGF0aW9uIiwib3NtX2lkIjo2MzMzMTQ1LCJsYXQiOiIzNC4wNTM2OTYwNSIsImxvbiI6Ii0xMTguMjQyOTIxMjE4MzMzOTUiLCJkaXNwbGF5X25hbWUiOiJMb3MgQW5nZWxlcyBDaXR5IEhhbGwsIDIwMCwgTm9ydGggU3ByaW5nIFN0cmVldCwgQ2l2aWMgQ2VudGVyLCBEb3dudG93biwgTG9zIEFuZ2VsZXMsIExvcyBBbmdlbGVzIENvdW50eSwgQ2FsaWZvcm5pYSwgOTAwMTIsIFVuaXRlZCBTdGF0ZXMiLCJhZGRyZXNzIjp7ImJ1aWxkaW5nIjoiTG9zIEFuZ2VsZXMgQ2l0eSBIYWxsIiwiaG91c2VfbnVtYmVyIjoiMjAwIiwicm9hZCI6Ik5vcnRoIFNwcmluZyBTdHJlZXQiLCJxdWFydGVyIjoiQ2l2aWMgQ2VudGVyIiwic3VidXJiIjoiRG93bnRvd24iLCJjaXR5IjoiTG9zIEFuZ2VsZXMiLCJjb3VudHkiOiJMb3MgQW5nZWxlcyBDb3VudHkiLCJzdGF0ZSI6IkNhbGlmb3JuaWEiLCJJU08zMTY2LTItbHZsNCI6IlVTLUNBIiwicG9zdGNvZGUiOiI5MDAxMiIsImNvdW50cnkiOiJVbml0ZWQgU3RhdGVzIiwiY291bnRyeV9jb2RlIjoidXMifSwiYm91bmRpbmdib3giOlsiMzQuMDUzMDE0MSIsIjM0LjA1NDM3MTMiLCItMTE4LjI0MzUzIiwiLTExOC4yNDIwMDUyIl19LCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjowLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsIm1zZyI6Im1lZXQgbWUgb25seSBpbiBwdWJsaWMiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDhUMDg6NTI6MjYuNzkzWiIsIm1hcmtldFByaWNlIjoxNjIuMTd9 @ 1eb966a6:e3eddf94
2024-11-09 13:18:54deleted
@ 1eb966a6:e3eddf94
2024-11-09 13:18:54deleted @ 1eb966a6:e3eddf94
2024-11-09 13:18:25deleted
@ 1eb966a6:e3eddf94
2024-11-09 13:18:25deleted @ b34f99f1:006b0fcc
2024-11-09 11:47:09deleted
@ b34f99f1:006b0fcc
2024-11-09 11:47:09deleted @ b34f99f1:006b0fcc
2024-11-09 11:43:11deleted
@ b34f99f1:006b0fcc
2024-11-09 11:43:11deleted @ b34f99f1:006b0fcc
2024-11-09 11:29:46deleted
@ b34f99f1:006b0fcc
2024-11-09 11:29:46deleted @ b34f99f1:006b0fcc
2024-11-09 11:25:16deleted
@ b34f99f1:006b0fcc
2024-11-09 11:25:16deleted @ fd208ee8:0fd927c1
2024-11-09 09:21:19## Drumroll, please.... In a previous article, I introduced the concept of [relay communities](nostr:naddr1qvzqqqr4gupzplfq3m5v3u5r0q9f255fdeyz8nyac6lagssx8zy4wugxjs8ajf7pqydhwumn8ghj7argv4nx7un9wd6zumn0wd68yvfwvdhk6tcpr3mhxue69uhhg6r9vd5hgctyv4kzumn0wd68yvfwvdhk6tcqp5cnwvesxcunjwpcxymrsvgwmj66e). The ink had barely dried, on that set of instructions, before one of my favorite Nostr devs, [ثعبان](nostr:nprofile1qythwumn8ghj7enjv4h8xtnwdaehgu339e3k7mf0qy88wumn8ghj7mn0wvhxcmmv9uqzqla9dawkjc4trc7dgf88trpsq2uxvhmmpkxua607nc5g6a634sv598gk68), rolled out the alpha version of a relay-community client. 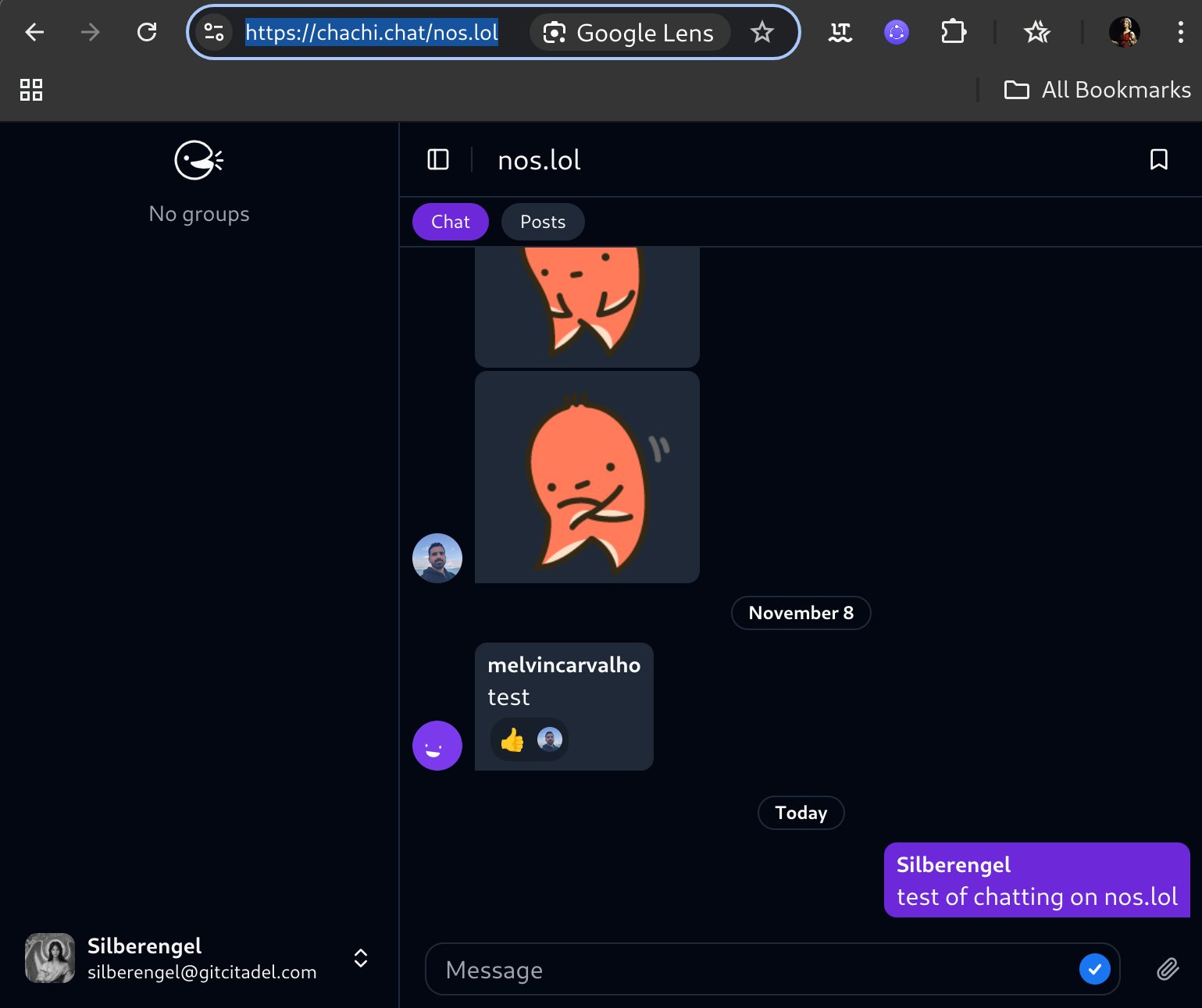 Obviously, it's still a bit of a construction site, but you can check out how it'd work, for your community, by test-driving the functionality on your own relay. Simply type _https://chachi.chat/_ followed by the name of your relay. For instance, one gigantic relay community, where nearly everyone can try out the functionality, is [nos.lol](https://chachi.chat/nos.lol). If your relay community does not require AUTH to read, anyone can pull your chatter into their own relay and respond to it there. That is because every chat entry is simply a kind 09 event, and unprotected events are not private data. For instance, I moderate one community [theforest.nostr1.com](https://chachi.chat/theforest.nostr1.com), that is openly readable, and that's probably where most of the chatter on [nostr.band](https://chachi.chat/relay.nostr.band) is coming from, as that relay is an aggregator of the content of many other relays. However, I have another community, [gitcitadel.nostr1.com](https://chachi.chat/gitcitadel.nostr1.com) that is AUTH-protected, whose content stays private to those allowed on that relay. Communities are where write-protected and AUTH relays are going to really shine, as they create an environment similar to Telegram, but where you control the dataset, you decide which types of events to support, and you design the client, the algos, the moderation, the visibility, etc. With communities, **the onboarding experience is seamless**: just get a browser extension and a nsec, login, start writing and posting, and _start receiving responses_. Active, chatty, well-moderated communities will be more attractive to onboard to, than chaotic, spammy, or empty communities. This means that you don't have to have the killer entry under "Posts" (where kind 11 and eventually kind 01 posts appear), just to get some interaction. Chat is the Great Equalizer. So, we're testing both setups, with [cloudfodder](nostr:nprofile1qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3eryvfwvdhk6tcqyp7vx29q3hdj4l0elxl800hlfjp538le09epsf7k9zj59ue2y37qu84upun) adjusting the relay faucet code and ثعبان is fiddling with the community client settings, to make the most-comfortable situation for both kinds.  ## This is the signal This #Chachi client, of course, is merely the first horse out of the gate. There are already other devs hacking away at variants of the same concept, such as [#Flotilla](https://flotilla.coracle.social/), I'm sure CloudFodder is also cooking, later versions of #Alexandria will integrate theforest community, and etc. etc. etc. It remains to be seen, how many new use cases can be dreamt up, with this new architecture, but I am quite certain, that this is the beginning of the end of Nostr 1.0. We are moving up and out, and away from the stultifying and limiting concept of Twitter 2.0, toward  Soon, we will enter Nostr 2.0. See you on the other side.
@ fd208ee8:0fd927c1
2024-11-09 09:21:19## Drumroll, please.... In a previous article, I introduced the concept of [relay communities](nostr:naddr1qvzqqqr4gupzplfq3m5v3u5r0q9f255fdeyz8nyac6lagssx8zy4wugxjs8ajf7pqydhwumn8ghj7argv4nx7un9wd6zumn0wd68yvfwvdhk6tcpr3mhxue69uhhg6r9vd5hgctyv4kzumn0wd68yvfwvdhk6tcqp5cnwvesxcunjwpcxymrsvgwmj66e). The ink had barely dried, on that set of instructions, before one of my favorite Nostr devs, [ثعبان](nostr:nprofile1qythwumn8ghj7enjv4h8xtnwdaehgu339e3k7mf0qy88wumn8ghj7mn0wvhxcmmv9uqzqla9dawkjc4trc7dgf88trpsq2uxvhmmpkxua607nc5g6a634sv598gk68), rolled out the alpha version of a relay-community client.  Obviously, it's still a bit of a construction site, but you can check out how it'd work, for your community, by test-driving the functionality on your own relay. Simply type _https://chachi.chat/_ followed by the name of your relay. For instance, one gigantic relay community, where nearly everyone can try out the functionality, is [nos.lol](https://chachi.chat/nos.lol). If your relay community does not require AUTH to read, anyone can pull your chatter into their own relay and respond to it there. That is because every chat entry is simply a kind 09 event, and unprotected events are not private data. For instance, I moderate one community [theforest.nostr1.com](https://chachi.chat/theforest.nostr1.com), that is openly readable, and that's probably where most of the chatter on [nostr.band](https://chachi.chat/relay.nostr.band) is coming from, as that relay is an aggregator of the content of many other relays. However, I have another community, [gitcitadel.nostr1.com](https://chachi.chat/gitcitadel.nostr1.com) that is AUTH-protected, whose content stays private to those allowed on that relay. Communities are where write-protected and AUTH relays are going to really shine, as they create an environment similar to Telegram, but where you control the dataset, you decide which types of events to support, and you design the client, the algos, the moderation, the visibility, etc. With communities, **the onboarding experience is seamless**: just get a browser extension and a nsec, login, start writing and posting, and _start receiving responses_. Active, chatty, well-moderated communities will be more attractive to onboard to, than chaotic, spammy, or empty communities. This means that you don't have to have the killer entry under "Posts" (where kind 11 and eventually kind 01 posts appear), just to get some interaction. Chat is the Great Equalizer. So, we're testing both setups, with [cloudfodder](nostr:nprofile1qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3eryvfwvdhk6tcqyp7vx29q3hdj4l0elxl800hlfjp538le09epsf7k9zj59ue2y37qu84upun) adjusting the relay faucet code and ثعبان is fiddling with the community client settings, to make the most-comfortable situation for both kinds.  ## This is the signal This #Chachi client, of course, is merely the first horse out of the gate. There are already other devs hacking away at variants of the same concept, such as [#Flotilla](https://flotilla.coracle.social/), I'm sure CloudFodder is also cooking, later versions of #Alexandria will integrate theforest community, and etc. etc. etc. It remains to be seen, how many new use cases can be dreamt up, with this new architecture, but I am quite certain, that this is the beginning of the end of Nostr 1.0. We are moving up and out, and away from the stultifying and limiting concept of Twitter 2.0, toward  Soon, we will enter Nostr 2.0. See you on the other side. @ a39d19ec:3d88f61e
2024-11-09 09:17:35##### What do you even print with it besides decorative objects? This kind of question still is a common one when talking about 3d printing. With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot. The second thing I show you is a "Swiss Keyholder" ## Swiss Keyholder There are many designs of such a Keyholder to download and print. As this is one of the first prints I have done in ABS back in 2014 on a "Up!Mini" 3d printer I can't find where I downloaded it. I like the slim design and that I don't have any "loose" keys in my pocket. It is just tidy in my pocket. This is probably the most used print of mine. Edit: You can download the file here: [Thingiverse](https://www.thingiverse.com/thing:98427) 
@ a39d19ec:3d88f61e
2024-11-09 09:17:35##### What do you even print with it besides decorative objects? This kind of question still is a common one when talking about 3d printing. With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot. The second thing I show you is a "Swiss Keyholder" ## Swiss Keyholder There are many designs of such a Keyholder to download and print. As this is one of the first prints I have done in ABS back in 2014 on a "Up!Mini" 3d printer I can't find where I downloaded it. I like the slim design and that I don't have any "loose" keys in my pocket. It is just tidy in my pocket. This is probably the most used print of mine. Edit: You can download the file here: [Thingiverse](https://www.thingiverse.com/thing:98427)  @ a95c6243:d345522c
2024-11-08 20:02:32*Und plötzlich weißt du: Es ist Zeit, etwas Neues zu beginnen und dem Zauber des Anfangs zu vertrauen. Meister Eckhart* **Schwarz, rot, gold leuchtet es im Kopf des Newsletters der deutschen Bundesregierung,** der mir freitags ins Postfach flattert. Rot, gelb und grün werden daneben sicher noch lange vielzitierte Farben sein, auch wenn diese nie geleuchtet haben. Die Ampel hat sich gerade selber den Stecker gezogen – und hinterlässt einen wirtschaftlichen und gesellschaftlichen Trümmerhaufen. **Mit einem bemerkenswerten [Timing](https://transition-news.org/donald-trump-grossmaul-oder-hoffnungstrager) hat die deutsche Regierungskoalition** am Tag des «Comebacks» von Donald Trump in den USA endlich ihr Scheitern besiegelt. Während der eine seinen Sieg bei den Präsidentschaftswahlen feierte, erwachten die anderen jäh aus ihrer [Selbsthypnose](https://ansage.org/schwer-traumatisiert-nach-trumps-sieg-dreht-die-politmediale-linksgruene-sekte-durch/) rund um Harris-Hype und Trump-Panik – mit teils erschreckenden [Auswüchsen](https://archive.is/7tDhY). Seit Mittwoch werden die Geschicke Deutschlands nun von einer rot-grünen Minderheitsregierung «geleitet» und man steuert auf Neuwahlen zu. **Das [Kindergarten](https://www.spiegel.de/politik/deutschland/christian-lindner-auch-die-fdp-will-wieder-einen-eigenen-wirtschaftsgipfel-abhalten-a-a8a4e868-10b1-426e-adb0-e5a6d42f7c46)-Gehabe um zwei konkurrierende Wirtschaftsgipfel letzte Woche** war bereits bezeichnend. In einem Strategiepapier gestand Finanzminister Lindner außerdem den «Absturz Deutschlands» ein und offenbarte, dass die wirtschaftlichen Probleme teilweise von der Ampel-Politik [«vorsätzlich herbeigeführt»](https://www.t-online.de/nachrichten/deutschland/innenpolitik/id_100522112/fdp-chef-lindner-und-sein-grundsatzpapier-die-scheidung-von-der-ampel-.html) worden seien. **Lindner und weitere FDP-Minister wurden also vom Bundeskanzler entlassen.** Verkehrs- und [Digitalminister Wissing](https://transition-news.org/raus-aus-der-komfortzone-es-lohnt-sich) trat flugs aus der FDP aus; deshalb darf er nicht nur im Amt bleiben, sondern hat zusätzlich noch das Justizministerium übernommen. Und mit [Jörg Kukies](https://norberthaering.de/news/joerg-kukies/) habe Scholz «seinen Lieblingsbock zum Obergärtner», sprich: Finanzminister befördert, meint Norbert Häring. **Es gebe keine Vertrauensbasis für die weitere Zusammenarbeit mit der FDP,** hatte der Kanzler erklärt, Lindner habe zu oft sein Vertrauen gebrochen. Am 15. Januar 2025 werde er daher im Bundestag die Vertrauensfrage stellen, was ggf. den Weg für vorgezogene Neuwahlen freimachen würde. **Apropos Vertrauen: Über die Hälfte der Bundesbürger glauben, dass sie ihre Meinung nicht frei sagen können.** Das ging erst kürzlich aus dem diesjährigen [«Freiheitsindex»](https://www.schwaebische.de/politik/forscher-beim-vertrauen-in-staat-und-medien-zerreisst-es-uns-gerade-3034357) hervor, einer Studie, die die Wechselwirkung zwischen Berichterstattung der Medien und subjektivem Freiheitsempfinden der Bürger misst. «Beim Vertrauen in Staat und Medien zerreißt es uns gerade», kommentierte dies der Leiter des Schweizer Unternehmens Media Tenor, das die Untersuchung zusammen mit dem Institut für Demoskopie Allensbach durchführt. **«Die absolute Mehrheit hat [absolut die Nase voll](https://archive.is/yRxwR)»,** titelte die *Bild* angesichts des «Ampel-Showdowns». Die Mehrheit wolle Neuwahlen und die Grünen sollten zuerst gehen, lasen wir dort. **Dass «Insolvenzminister» Robert Habeck heute seine Kandidatur für das Kanzleramt verkündet hat,** kann nur als Teil der politmedialen Realitätsverweigerung verstanden werden. Wer allerdings denke, schlimmer als in Zeiten der Ampel könne es nicht mehr werden, sei reichlich optimistisch, schrieb Uwe Froschauer bei *Manova*. Und er kenne [Friedrich Merz](https://www.manova.news/artikel/der-kriegsgeile-blackrocker) schlecht, der sich schon jetzt rhetorisch auf seine Rolle als oberster Feldherr Deutschlands vorbereite. **Was also tun? Der Schweizer Verein [«Losdemokratie»](https://zeitpunkt.ch/node/40968) will eine Volksinitiative lancieren,** um die Bestimmung von Parlamentsmitgliedern per Los einzuführen. Das Losverfahren sorge für mehr Demokratie, denn als Alternative zum Wahlverfahren garantiere es eine breitere Beteiligung und repräsentativere Parlamente. Ob das ein Weg ist, sei dahingestellt. **In jedem Fall wird es notwendig sein, unsere Bemühungen um [Freiheit und Selbstbestimmung](https://transition-news.org/alternative-medien-in-der-krise-zensur-kontrollverlust-und-die-suche-nach)** zu verstärken. Mehr Unabhängigkeit von staatlichen und zentralen Institutionen – also die Suche nach dezentralen Lösungsansätzen – gehört dabei sicher zu den Möglichkeiten. Das gilt sowohl für jede/n Einzelne/n als auch für Entitäten wie die alternativen Medien. --- Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/es-kann-nur-besser-werden-aber-wie)* erschienen.
@ a95c6243:d345522c
2024-11-08 20:02:32*Und plötzlich weißt du: Es ist Zeit, etwas Neues zu beginnen und dem Zauber des Anfangs zu vertrauen. Meister Eckhart* **Schwarz, rot, gold leuchtet es im Kopf des Newsletters der deutschen Bundesregierung,** der mir freitags ins Postfach flattert. Rot, gelb und grün werden daneben sicher noch lange vielzitierte Farben sein, auch wenn diese nie geleuchtet haben. Die Ampel hat sich gerade selber den Stecker gezogen – und hinterlässt einen wirtschaftlichen und gesellschaftlichen Trümmerhaufen. **Mit einem bemerkenswerten [Timing](https://transition-news.org/donald-trump-grossmaul-oder-hoffnungstrager) hat die deutsche Regierungskoalition** am Tag des «Comebacks» von Donald Trump in den USA endlich ihr Scheitern besiegelt. Während der eine seinen Sieg bei den Präsidentschaftswahlen feierte, erwachten die anderen jäh aus ihrer [Selbsthypnose](https://ansage.org/schwer-traumatisiert-nach-trumps-sieg-dreht-die-politmediale-linksgruene-sekte-durch/) rund um Harris-Hype und Trump-Panik – mit teils erschreckenden [Auswüchsen](https://archive.is/7tDhY). Seit Mittwoch werden die Geschicke Deutschlands nun von einer rot-grünen Minderheitsregierung «geleitet» und man steuert auf Neuwahlen zu. **Das [Kindergarten](https://www.spiegel.de/politik/deutschland/christian-lindner-auch-die-fdp-will-wieder-einen-eigenen-wirtschaftsgipfel-abhalten-a-a8a4e868-10b1-426e-adb0-e5a6d42f7c46)-Gehabe um zwei konkurrierende Wirtschaftsgipfel letzte Woche** war bereits bezeichnend. In einem Strategiepapier gestand Finanzminister Lindner außerdem den «Absturz Deutschlands» ein und offenbarte, dass die wirtschaftlichen Probleme teilweise von der Ampel-Politik [«vorsätzlich herbeigeführt»](https://www.t-online.de/nachrichten/deutschland/innenpolitik/id_100522112/fdp-chef-lindner-und-sein-grundsatzpapier-die-scheidung-von-der-ampel-.html) worden seien. **Lindner und weitere FDP-Minister wurden also vom Bundeskanzler entlassen.** Verkehrs- und [Digitalminister Wissing](https://transition-news.org/raus-aus-der-komfortzone-es-lohnt-sich) trat flugs aus der FDP aus; deshalb darf er nicht nur im Amt bleiben, sondern hat zusätzlich noch das Justizministerium übernommen. Und mit [Jörg Kukies](https://norberthaering.de/news/joerg-kukies/) habe Scholz «seinen Lieblingsbock zum Obergärtner», sprich: Finanzminister befördert, meint Norbert Häring. **Es gebe keine Vertrauensbasis für die weitere Zusammenarbeit mit der FDP,** hatte der Kanzler erklärt, Lindner habe zu oft sein Vertrauen gebrochen. Am 15. Januar 2025 werde er daher im Bundestag die Vertrauensfrage stellen, was ggf. den Weg für vorgezogene Neuwahlen freimachen würde. **Apropos Vertrauen: Über die Hälfte der Bundesbürger glauben, dass sie ihre Meinung nicht frei sagen können.** Das ging erst kürzlich aus dem diesjährigen [«Freiheitsindex»](https://www.schwaebische.de/politik/forscher-beim-vertrauen-in-staat-und-medien-zerreisst-es-uns-gerade-3034357) hervor, einer Studie, die die Wechselwirkung zwischen Berichterstattung der Medien und subjektivem Freiheitsempfinden der Bürger misst. «Beim Vertrauen in Staat und Medien zerreißt es uns gerade», kommentierte dies der Leiter des Schweizer Unternehmens Media Tenor, das die Untersuchung zusammen mit dem Institut für Demoskopie Allensbach durchführt. **«Die absolute Mehrheit hat [absolut die Nase voll](https://archive.is/yRxwR)»,** titelte die *Bild* angesichts des «Ampel-Showdowns». Die Mehrheit wolle Neuwahlen und die Grünen sollten zuerst gehen, lasen wir dort. **Dass «Insolvenzminister» Robert Habeck heute seine Kandidatur für das Kanzleramt verkündet hat,** kann nur als Teil der politmedialen Realitätsverweigerung verstanden werden. Wer allerdings denke, schlimmer als in Zeiten der Ampel könne es nicht mehr werden, sei reichlich optimistisch, schrieb Uwe Froschauer bei *Manova*. Und er kenne [Friedrich Merz](https://www.manova.news/artikel/der-kriegsgeile-blackrocker) schlecht, der sich schon jetzt rhetorisch auf seine Rolle als oberster Feldherr Deutschlands vorbereite. **Was also tun? Der Schweizer Verein [«Losdemokratie»](https://zeitpunkt.ch/node/40968) will eine Volksinitiative lancieren,** um die Bestimmung von Parlamentsmitgliedern per Los einzuführen. Das Losverfahren sorge für mehr Demokratie, denn als Alternative zum Wahlverfahren garantiere es eine breitere Beteiligung und repräsentativere Parlamente. Ob das ein Weg ist, sei dahingestellt. **In jedem Fall wird es notwendig sein, unsere Bemühungen um [Freiheit und Selbstbestimmung](https://transition-news.org/alternative-medien-in-der-krise-zensur-kontrollverlust-und-die-suche-nach)** zu verstärken. Mehr Unabhängigkeit von staatlichen und zentralen Institutionen – also die Suche nach dezentralen Lösungsansätzen – gehört dabei sicher zu den Möglichkeiten. Das gilt sowohl für jede/n Einzelne/n als auch für Entitäten wie die alternativen Medien. --- Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/es-kann-nur-besser-werden-aber-wie)* erschienen. @ fd208ee8:0fd927c1
2024-11-08 10:27:40## You have no idea I regularly read comments from people, on here, wondering how it's possible to marry -- or even simply be friends! -- with someone who doesn't agree with you on politics. I see this sentiment expressed quite often, usually in the context of Bitcoin, or whatever _pig is currently being chased through the village_, as they say around here.  It seems rather sensible, but I don't think it's as hard, as people make it out to be. Further, I think it's a dangerous precondition to set, for your interpersonal relationships, because the political field is constantly in flux. If you determine who you will love, by their opinions, do you stop loving them if their opinions change, or if the opinions they have become irrelevant and a new set of opinions are needed -- and their new ones don't match your new ones? We could see this happen to relationships en masse, during the Covid Era, and I think it happens every day, in a slow grind toward the disintegration of interpersonal discourse. I suspect many people do stop loving, at that point, as they never really loved the other person for their own sake, they loved the other person because they thought the other person was exactly like they are. But no two people are alike, and the longer you are in a relationship with someone else, the more the initial giddiness wears off and the trials and tribulations add up, the more you notice how very different you actually are. This is the point, where best friends and romantic couples say, _We just grew apart._ But you were always apart. You were always two different people. You just didn't notice, until now.  I've also always been surprised at how many same-party relationships disintegrate because of some disagreement over some particular detail of some particular topic, that they generally agree on. To me, it seems like an irrelevant side-topic, but _they can't stand to be with this person_... and they stomp off. So, I tend to think that it's less that opinions need to align to each other, but rather that opinions need to align in accordance with the level of interpersonal tolerance they can bring into the relationship. ## I was raised by relaxed revolutionaries Maybe I see things this way because my parents come from two diverging political, cultural, national, and ethnic backgrounds, and are prone to disagreeing about a lot of "important" (to people outside their marriage) things, but still have one of the healthiest, most-fruitful, and most long-running marriages of anyone I know, from that generation. My parents, you see, aren't united by their opinions. They're united by their relationship, which is something _outside_ of opinions. Beyond opinions. Relationships are what turn two different people into one, cohesive unit, so that they slowly grow together. Eventually, even their faces merge, and their biological clocks tick to the same rhythm. They eventually become one entity that contains differing opinions about the same topics. It's like magic, but it's the result of a mindset, not a worldview. Or, as I like to quip: > The best way to stay married, is to not get divorced.  My parents simply determined early on, that they would stay together, and whenever they would find that they disagreed on something that _didn't directly pertain to their day-to-day existence with each other_ they would just agree-to-disagree about that, or roll their eyes, and move on. You do you. Live and let live. My parents have some of the most strongly held personal opinions of any people I've ever met, but they're also incredibly tolerant and can get along with nearly anyone, so their friends are a confusing hodgepodge of _people we liked and found interesting enough to keep around_. Which makes their house parties really fun, and highly unusual, in this day and age of mutual-damnation across the aisle.  The things that did affect them, directly, like which school the children should attend or which country they should live in, etc. were things they'd sit down and discuss, and somehow one opinion would emerge, and they'd again... move on. And that's how my husband and I also live our lives, and it's been working surprisingly well. No topics are off-limits to discussion (so long as you don't drone on for too long), nobody has to give up deeply held beliefs, or stop agitating for the political decisions they prefer. You see, we didn't like that the other always had the same opinion. We liked that the other always held their opinions strongly. That they were passionate about their opinions. That they were willing to voice their opinions; sacrifice to promote their opinions. And that they didn't let anyone browbeat or cow them, for their opinions, not even their best friends or their spouse. But that they were open to listening to the other side, and trying to wrap their mind around the possibility that they _might just be wrong about something_.  We married each other because we knew: this person really cares, this person has thought this through, and they're in it, to win it. What "it" is, is mostly irrelevant, so long as it doesn't entail torturing small animals in the basement, or raising the children on a diet of Mountain Dew and porn, or something. Live and let live. At least, it's never boring. At least, there's always something to ~~argue~~ talk about. At least, we never think... we've just grown apart.
@ fd208ee8:0fd927c1
2024-11-08 10:27:40## You have no idea I regularly read comments from people, on here, wondering how it's possible to marry -- or even simply be friends! -- with someone who doesn't agree with you on politics. I see this sentiment expressed quite often, usually in the context of Bitcoin, or whatever _pig is currently being chased through the village_, as they say around here.  It seems rather sensible, but I don't think it's as hard, as people make it out to be. Further, I think it's a dangerous precondition to set, for your interpersonal relationships, because the political field is constantly in flux. If you determine who you will love, by their opinions, do you stop loving them if their opinions change, or if the opinions they have become irrelevant and a new set of opinions are needed -- and their new ones don't match your new ones? We could see this happen to relationships en masse, during the Covid Era, and I think it happens every day, in a slow grind toward the disintegration of interpersonal discourse. I suspect many people do stop loving, at that point, as they never really loved the other person for their own sake, they loved the other person because they thought the other person was exactly like they are. But no two people are alike, and the longer you are in a relationship with someone else, the more the initial giddiness wears off and the trials and tribulations add up, the more you notice how very different you actually are. This is the point, where best friends and romantic couples say, _We just grew apart._ But you were always apart. You were always two different people. You just didn't notice, until now.  I've also always been surprised at how many same-party relationships disintegrate because of some disagreement over some particular detail of some particular topic, that they generally agree on. To me, it seems like an irrelevant side-topic, but _they can't stand to be with this person_... and they stomp off. So, I tend to think that it's less that opinions need to align to each other, but rather that opinions need to align in accordance with the level of interpersonal tolerance they can bring into the relationship. ## I was raised by relaxed revolutionaries Maybe I see things this way because my parents come from two diverging political, cultural, national, and ethnic backgrounds, and are prone to disagreeing about a lot of "important" (to people outside their marriage) things, but still have one of the healthiest, most-fruitful, and most long-running marriages of anyone I know, from that generation. My parents, you see, aren't united by their opinions. They're united by their relationship, which is something _outside_ of opinions. Beyond opinions. Relationships are what turn two different people into one, cohesive unit, so that they slowly grow together. Eventually, even their faces merge, and their biological clocks tick to the same rhythm. They eventually become one entity that contains differing opinions about the same topics. It's like magic, but it's the result of a mindset, not a worldview. Or, as I like to quip: > The best way to stay married, is to not get divorced.  My parents simply determined early on, that they would stay together, and whenever they would find that they disagreed on something that _didn't directly pertain to their day-to-day existence with each other_ they would just agree-to-disagree about that, or roll their eyes, and move on. You do you. Live and let live. My parents have some of the most strongly held personal opinions of any people I've ever met, but they're also incredibly tolerant and can get along with nearly anyone, so their friends are a confusing hodgepodge of _people we liked and found interesting enough to keep around_. Which makes their house parties really fun, and highly unusual, in this day and age of mutual-damnation across the aisle.  The things that did affect them, directly, like which school the children should attend or which country they should live in, etc. were things they'd sit down and discuss, and somehow one opinion would emerge, and they'd again... move on. And that's how my husband and I also live our lives, and it's been working surprisingly well. No topics are off-limits to discussion (so long as you don't drone on for too long), nobody has to give up deeply held beliefs, or stop agitating for the political decisions they prefer. You see, we didn't like that the other always had the same opinion. We liked that the other always held their opinions strongly. That they were passionate about their opinions. That they were willing to voice their opinions; sacrifice to promote their opinions. And that they didn't let anyone browbeat or cow them, for their opinions, not even their best friends or their spouse. But that they were open to listening to the other side, and trying to wrap their mind around the possibility that they _might just be wrong about something_.  We married each other because we knew: this person really cares, this person has thought this through, and they're in it, to win it. What "it" is, is mostly irrelevant, so long as it doesn't entail torturing small animals in the basement, or raising the children on a diet of Mountain Dew and porn, or something. Live and let live. At least, it's never boring. At least, there's always something to ~~argue~~ talk about. At least, we never think... we've just grown apart. @ 13351007:eccd002a
2024-11-08 05:32:41eyJfaWQiOiI0OTNkNDQyNS01YTRiLTQ2YjYtYjFhNC0yZTEyNjZlYTEyNDYiLCJwdWJsaWNLZXkiOiIxZWI5NjZhNmEwMjE4YWJhNTIwYWFhYzkzYmU3ZGQ4YmYzODMwZmM3NzEwYmM4MGNhZWEzYTZhNWUzZWRkZjk0IiwidXNlcm5hbWUiOiJoYW5rIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiTkFUSU9OQUxfQkFOSyIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjoiMyIsImZpeGVkUHJpY2UiOiIiLCJtaW5BbW91bnQiOiIxMDAiLCJtYXhBbW91bnQiOiIiLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiZmFzdCBhbmQgYmVzdCB0cmFkZXIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOiIiLCJmaXJzdFRpbWVMaW1pdEFzc2V0IjoiIiwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMS0wOFQwNTozMjo0MS44MzZaIiwibWFya2V0UHJpY2UiOjE2NC4xM30=
@ 13351007:eccd002a
2024-11-08 05:32:41eyJfaWQiOiI0OTNkNDQyNS01YTRiLTQ2YjYtYjFhNC0yZTEyNjZlYTEyNDYiLCJwdWJsaWNLZXkiOiIxZWI5NjZhNmEwMjE4YWJhNTIwYWFhYzkzYmU3ZGQ4YmYzODMwZmM3NzEwYmM4MGNhZWEzYTZhNWUzZWRkZjk0IiwidXNlcm5hbWUiOiJoYW5rIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiTkFUSU9OQUxfQkFOSyIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjoiMyIsImZpeGVkUHJpY2UiOiIiLCJtaW5BbW91bnQiOiIxMDAiLCJtYXhBbW91bnQiOiIiLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiZmFzdCBhbmQgYmVzdCB0cmFkZXIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOiIiLCJmaXJzdFRpbWVMaW1pdEFzc2V0IjoiIiwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMS0wOFQwNTozMjo0MS44MzZaIiwibWFya2V0UHJpY2UiOjE2NC4xM30= @ 4ba8e86d:89d32de4
2024-11-07 13:56:21Tutorial feito por Grom mestre⚡poste original abaixo: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/240277/tutorial-criando-e-acessando-sua-conta-de-email-pela-i2p?show=240277#q240277 Bom dia/tarde/noite a todos os camaradas. Seguindo a nossa série de tutoriais referentes a tecnologias essenciais para a segurança e o anonimato dos usuários, sendo as primeiras a openPGP e a I2P, lhes apresento mais uma opção para expandir os seus conhecimentos da DW. Muitos devem conhecer os serviços de mail na onion como DNMX e mail2tor, mas e que tal um serviço de email pela I2P. Nesse tutorial eu vou mostrar a vocês como criar a sua primeira conta no hq.postman.i2p e a acessar essa conta. É importante que vocês tenham lido a minha primeira série de tutoriais a respeito de como instalar, configurar e navegar pela I2P nostr:nevent1qqsyjcz2w0e6d6dcdeprhuuarw4aqkw730y542dzlwxwssneq3mwpaspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsyp5vcq Esse tutorial é um pré-requisito para o seguinte e portanto recomendo que leia-os antes de prosseguir com o seguinte tutorial. O tutorial de Kleopatra nostr:nevent1qqs8h7vsn5j6qh35949sa60dms4fneussmv9jd76n24lsmtz24k0xlqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgecq8f7 é complementar dado que é extremamente recomendado assinar e criptografar as mensagens que seguem por emails pela DW. Sem mais delongas, vamos ao tutorial de fato. ## 1. Criando uma conta de email no hq.postman Relembrando: Esse tutorial considera que você já tenha acesso à I2P. Entre no seu navegador e acesse o endereço hq.postman.i2p. O roteador provavelmente já contém esse endereço no seu addressbook e não haverá a necessidade de inserir o endereço b32 completo. Após entrar no site vá para a página '1 - Creating a mailbox' https://image.nostr.build/d850379fe315d2abab71430949b06d3fa49366d91df4c9b00a4a8367d53fcca3.jpg Nessa página, insira as credenciais de sua preferências nos campos do formulário abaixo. Lembre-se que o seu endereço de email aceita apenas letras e números. Clique em 'Proceed' depois que preencher todos os campos. https://image.nostr.build/670dfda7264db393e48391f217e60a2eb87d85c2729360c8ef6fe0cf52508ab4.jpg Uma página vai aparecer pedindo para confirmar as credenciais da sua nova conta. Se tudo estiver certo apenas clique em 'Confirm and Create Mailbox'. Se tudo ocorrer como conforme haverá uma confirmação de que a sua nova conta foi criada com sucesso. Após isso aguarde por volta de 5 minutos antes de tentar acessá-la, para que haja tempo suficiente para o servidor atualizar o banco de dados. https://image.nostr.build/ec58fb826bffa60791fedfd9c89a25d592ac3d11645b270c936c60a7c59c067f.jpg https://image.nostr.build/a2b7710d1e3cbb36431acb9055fd62937986b4da4b1a1bbb06d3f3cb1f544fd3.jpg Pronto! Sua nova conta de email na I2P foi criada. Agora vamos para a próxima etapa: como acessar a sua conta via um cliente de email. ## 2. Configurando os túneis cliente de SMTP e POP3 O hq.postman não possui um cliente web que nos permite acessar a nossa conta pelo navegador. Para isso precisamos usar um cliente como Thunderbird e configurar os túneis cliente no I2Pd que serão necessários para o Thunderbird se comunicar com o servidor pela I2P. Caso não tenha instalado o Thunderbird ainda, faça-o agora antes de prosseguir. Vamos configurar os túneis cliente do servidor de email no nosso roteador. Para isso abra um terminal ou o seu gestor de arquivos e vá para a pasta de configuração de túneis do I2P. Em Linux esse diretório se localiza em /etc/i2pd/tunnels.d. Em Windows, essa pasta se localiza em C:\users\user\APPDATA\i2pd. Na pasta tunnels.d crie dois arquivos: smtp.postman.conf e pop-postman.conf. Lembre-se que em Linux você precisa de permissões de root para escrever na pasta de configuração. Use o comando sudoedit <nome_do_arquivo> para isso. Edite-os conforme as imagens a seguir: Arquivo pop-postman.conf https://image.nostr.build/7e03505c8bc3b632ca5db1f8eaefc6cecb4743cd2096d211dd90bbdc16fe2593.jpg Arquivo smtp-postman.conf https://image.nostr.build/2d06c021841dedd6000c9fc2a641ed519b3be3c6125000b188842cd0a5af3d16.jpg Salve os arquivos e reinicie o serviço do I2Pd. Em Linux isso é feito pelo comando: ``` sudo systemctl restart i2pd ``` Entre no Webconsole do I2Pd pelo navegador (localhost:7070) e na seção I2P Tunnels, verifique se os túneis pop-postman e smtp-postman foram criados, caso contrário verifique se há algum erro nos arquivos e reinicie o serviço. Com os túneis cliente criados, vamos agora configurar o Thunderbird ## 3. Configurando o Thunderbird para acessar a nossa conta Abra o Thunderbird e clique em criar uma nova conta de email. Se você não tiver nenhum conta previamente presente nele você vai ser diretamente recebido pela janela de criação de conta a seguir. https://image.nostr.build/e9509d7bd30623716ef9adcad76c1d465f5bc3d5840e0c35fe4faa85740f41b4.jpg https://image.nostr.build/688b59b8352a17389902ec1e99d7484e310d7d287491b34f562b8cdd9dbe8a99.jpg Coloque as suas credenciais, mas não clique ainda em Continuar. Clique antes em Configure Manually, já que precisamos configurar manualmente os servidores de SMTP e POP3 para, respectivamente, enviar e receber mensagens. Preencha os campos como na imagem a seguir. Detalhe: Não coloque o seu endereço completo com o @mail.i2p, apenas o nome da sua conta. https://image.nostr.build/4610b0315c0a3b741965d3d7c1e4aff6425a167297e323ba8490f4325f40cdcc.jpg Clique em Re-test para verificar a integridade da conexão. Se tudo estiver certo uma mensagem irá aparecer avisando que as configurações do servidores estão corretas. Clique em Done assim que estiver pronto para prosseguir. https://image.nostr.build/8a47bb292f94b0d9d474d4d4a134f8d73afb84ecf1d4c0a7eb6366d46bf3973a.jpg A seguinte mensagem vai aparecer alertando que não estamos usando criptografia no envio das credenciais. Não há problema nenhum aqui, pois a I2P está garantindo toda a proteção e anonimato dos nossos dados, o que dispensa a necessidade de uso de TLS ou qualquer tecnologia similar nas camadas acima. Marque a opção 'I Understand the risks' e clique em 'Continue' https://image.nostr.build/9c1bf585248773297d2cb1d9705c1be3bd815e2be85d4342227f1db2f13a9cc6.jpg E por fim, se tudo ocorreu como devido sua conta será criada com sucesso e você agora será capaz de enviar e receber emails pela I2P usando essa conta. https://image.nostr.build/8ba7f2c160453c9bfa172fa9a30b642a7ee9ae3eeb9b78b4dc24ce25aa2c7ecc.jpg ## 4. Observações e considerações finais Como informado pelo próprio site do hq.postman, o domínio @mail.i2p serve apenas para emails enviados dentro da I2P. Emails enviados pela surface devem usar o domínio @i2pmai.org. É imprescindível que você saiba usar o PGP para assinar e criptografar as suas mensagens, dado que provavelmente as mensagens não são armazenadas de forma criptografada enquanto elas estão armazenadas no servidor. Como o protocolo POP3 delete as mensagens no imediato momento em que você as recebe, não há necessidade de fazer qualquer limpeza na sua conta de forma manual. Por fim, espero que esse tutorial tenha sido útil para vocês. Que seu conhecimento tenha expandido ainda mais com as informações trazidas aqui. Até a próxima.
@ 4ba8e86d:89d32de4
2024-11-07 13:56:21Tutorial feito por Grom mestre⚡poste original abaixo: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/240277/tutorial-criando-e-acessando-sua-conta-de-email-pela-i2p?show=240277#q240277 Bom dia/tarde/noite a todos os camaradas. Seguindo a nossa série de tutoriais referentes a tecnologias essenciais para a segurança e o anonimato dos usuários, sendo as primeiras a openPGP e a I2P, lhes apresento mais uma opção para expandir os seus conhecimentos da DW. Muitos devem conhecer os serviços de mail na onion como DNMX e mail2tor, mas e que tal um serviço de email pela I2P. Nesse tutorial eu vou mostrar a vocês como criar a sua primeira conta no hq.postman.i2p e a acessar essa conta. É importante que vocês tenham lido a minha primeira série de tutoriais a respeito de como instalar, configurar e navegar pela I2P nostr:nevent1qqsyjcz2w0e6d6dcdeprhuuarw4aqkw730y542dzlwxwssneq3mwpaspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsyp5vcq Esse tutorial é um pré-requisito para o seguinte e portanto recomendo que leia-os antes de prosseguir com o seguinte tutorial. O tutorial de Kleopatra nostr:nevent1qqs8h7vsn5j6qh35949sa60dms4fneussmv9jd76n24lsmtz24k0xlqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgecq8f7 é complementar dado que é extremamente recomendado assinar e criptografar as mensagens que seguem por emails pela DW. Sem mais delongas, vamos ao tutorial de fato. ## 1. Criando uma conta de email no hq.postman Relembrando: Esse tutorial considera que você já tenha acesso à I2P. Entre no seu navegador e acesse o endereço hq.postman.i2p. O roteador provavelmente já contém esse endereço no seu addressbook e não haverá a necessidade de inserir o endereço b32 completo. Após entrar no site vá para a página '1 - Creating a mailbox' https://image.nostr.build/d850379fe315d2abab71430949b06d3fa49366d91df4c9b00a4a8367d53fcca3.jpg Nessa página, insira as credenciais de sua preferências nos campos do formulário abaixo. Lembre-se que o seu endereço de email aceita apenas letras e números. Clique em 'Proceed' depois que preencher todos os campos. https://image.nostr.build/670dfda7264db393e48391f217e60a2eb87d85c2729360c8ef6fe0cf52508ab4.jpg Uma página vai aparecer pedindo para confirmar as credenciais da sua nova conta. Se tudo estiver certo apenas clique em 'Confirm and Create Mailbox'. Se tudo ocorrer como conforme haverá uma confirmação de que a sua nova conta foi criada com sucesso. Após isso aguarde por volta de 5 minutos antes de tentar acessá-la, para que haja tempo suficiente para o servidor atualizar o banco de dados. https://image.nostr.build/ec58fb826bffa60791fedfd9c89a25d592ac3d11645b270c936c60a7c59c067f.jpg https://image.nostr.build/a2b7710d1e3cbb36431acb9055fd62937986b4da4b1a1bbb06d3f3cb1f544fd3.jpg Pronto! Sua nova conta de email na I2P foi criada. Agora vamos para a próxima etapa: como acessar a sua conta via um cliente de email. ## 2. Configurando os túneis cliente de SMTP e POP3 O hq.postman não possui um cliente web que nos permite acessar a nossa conta pelo navegador. Para isso precisamos usar um cliente como Thunderbird e configurar os túneis cliente no I2Pd que serão necessários para o Thunderbird se comunicar com o servidor pela I2P. Caso não tenha instalado o Thunderbird ainda, faça-o agora antes de prosseguir. Vamos configurar os túneis cliente do servidor de email no nosso roteador. Para isso abra um terminal ou o seu gestor de arquivos e vá para a pasta de configuração de túneis do I2P. Em Linux esse diretório se localiza em /etc/i2pd/tunnels.d. Em Windows, essa pasta se localiza em C:\users\user\APPDATA\i2pd. Na pasta tunnels.d crie dois arquivos: smtp.postman.conf e pop-postman.conf. Lembre-se que em Linux você precisa de permissões de root para escrever na pasta de configuração. Use o comando sudoedit <nome_do_arquivo> para isso. Edite-os conforme as imagens a seguir: Arquivo pop-postman.conf https://image.nostr.build/7e03505c8bc3b632ca5db1f8eaefc6cecb4743cd2096d211dd90bbdc16fe2593.jpg Arquivo smtp-postman.conf https://image.nostr.build/2d06c021841dedd6000c9fc2a641ed519b3be3c6125000b188842cd0a5af3d16.jpg Salve os arquivos e reinicie o serviço do I2Pd. Em Linux isso é feito pelo comando: ``` sudo systemctl restart i2pd ``` Entre no Webconsole do I2Pd pelo navegador (localhost:7070) e na seção I2P Tunnels, verifique se os túneis pop-postman e smtp-postman foram criados, caso contrário verifique se há algum erro nos arquivos e reinicie o serviço. Com os túneis cliente criados, vamos agora configurar o Thunderbird ## 3. Configurando o Thunderbird para acessar a nossa conta Abra o Thunderbird e clique em criar uma nova conta de email. Se você não tiver nenhum conta previamente presente nele você vai ser diretamente recebido pela janela de criação de conta a seguir. https://image.nostr.build/e9509d7bd30623716ef9adcad76c1d465f5bc3d5840e0c35fe4faa85740f41b4.jpg https://image.nostr.build/688b59b8352a17389902ec1e99d7484e310d7d287491b34f562b8cdd9dbe8a99.jpg Coloque as suas credenciais, mas não clique ainda em Continuar. Clique antes em Configure Manually, já que precisamos configurar manualmente os servidores de SMTP e POP3 para, respectivamente, enviar e receber mensagens. Preencha os campos como na imagem a seguir. Detalhe: Não coloque o seu endereço completo com o @mail.i2p, apenas o nome da sua conta. https://image.nostr.build/4610b0315c0a3b741965d3d7c1e4aff6425a167297e323ba8490f4325f40cdcc.jpg Clique em Re-test para verificar a integridade da conexão. Se tudo estiver certo uma mensagem irá aparecer avisando que as configurações do servidores estão corretas. Clique em Done assim que estiver pronto para prosseguir. https://image.nostr.build/8a47bb292f94b0d9d474d4d4a134f8d73afb84ecf1d4c0a7eb6366d46bf3973a.jpg A seguinte mensagem vai aparecer alertando que não estamos usando criptografia no envio das credenciais. Não há problema nenhum aqui, pois a I2P está garantindo toda a proteção e anonimato dos nossos dados, o que dispensa a necessidade de uso de TLS ou qualquer tecnologia similar nas camadas acima. Marque a opção 'I Understand the risks' e clique em 'Continue' https://image.nostr.build/9c1bf585248773297d2cb1d9705c1be3bd815e2be85d4342227f1db2f13a9cc6.jpg E por fim, se tudo ocorreu como devido sua conta será criada com sucesso e você agora será capaz de enviar e receber emails pela I2P usando essa conta. https://image.nostr.build/8ba7f2c160453c9bfa172fa9a30b642a7ee9ae3eeb9b78b4dc24ce25aa2c7ecc.jpg ## 4. Observações e considerações finais Como informado pelo próprio site do hq.postman, o domínio @mail.i2p serve apenas para emails enviados dentro da I2P. Emails enviados pela surface devem usar o domínio @i2pmai.org. É imprescindível que você saiba usar o PGP para assinar e criptografar as suas mensagens, dado que provavelmente as mensagens não são armazenadas de forma criptografada enquanto elas estão armazenadas no servidor. Como o protocolo POP3 delete as mensagens no imediato momento em que você as recebe, não há necessidade de fazer qualquer limpeza na sua conta de forma manual. Por fim, espero que esse tutorial tenha sido útil para vocês. Que seu conhecimento tenha expandido ainda mais com as informações trazidas aqui. Até a próxima. @ fd208ee8:0fd927c1
2024-11-07 07:28:06## The newspaper barons are all into crypto, now Watching the outsized-impact we crypto enthusiasts (I'm including Bitcoin in that category), had on the 2024 USA presidential election, was a sobering affair. At the moment, our impact is primarily over the voting box, but, already, indirectly, (over Elon Musik, Donald Trump, and Jack Dorsey, etc.) through our sheer wealth (and the ingenuity that brought us that wealth) being able to influence the voting population, by changing/shifting the communications channels and influencing what is written there. Elon even reached deep into his foreign-learned bag of political tricks and started [handing out money, directly](https://www.bbc.com/news/articles/crlnjzzk919o), to petition signers.  ## Survival of the fittest, ongoing Now, you all know that I have full respect for an expert player, when I see one, so no hating the hustle, from my side. We all play the hand we are dealt, and the political game is now such a pigsty, that you have to get a bit dirty, to have a chance at winning. Trying to stay neat and above the fray cost Republicans the last election.  It was the most dramatic display of the greatest power following the best money, that has been seen, since the Medici family began minting gold coins. The entire world is in shock. Change is upon us. He who has the best money, makes the rules. On a smaller, but not insignificant scale, private wealth and access to Bitcoin funding, have allowed quite a few of us Nostriches, to dedicate time and energy toward promoting and developing the New Internet. Whereas, other people's hobby is increasingly the night shift at the gas station, or doing something mind-numbing, to escape the realities of their current economic misery. You don't need money to be here, but you can spend more time here, if you have money. And we are here, writing the rules. We call them NIPs.  ## Same ole, same ole But back to us Bitcoiners... I increasingly don't see us morally any different than the clever people crowding into any safe asset, during any financial crisis. Like the people who bought agricultural land, gold, and Swiss Francs, before the Reichsmark melted down. The people who had that stuff, mostly managed to keep it, and their children and grandchildren have inherited it. Or they managed to marry back into families, that have done so, by remaining in the same social class, through beauty or talent.  We Bitcoiners have a good narrative to go along with our flight to economic safety, but everyone has that narrative. Humans have a conscience and need to justify their own actions, to themselves. I'm also a goldbug, you see, and a stockholder, and all three assets are rife with the same virtuous narrative. ## How do we save our financial behinds, without being evil? Some people are simply more situationally aware and have more agency, by nature and circumstances, and they adapt faster. It's not mere intelligence, rather, it also requires a willingness to act and take risks. There's an element of chance to it, but it's still always the same types of people ending up with the assets, with the winners slightly shifting with each round, due to evolution and changes in the environment. Charity was invented, to get such people to willingly share their assets, or the fruits of their assets, for the common good. So, rather than fret over the morality of the asset, itself, the better response is to consider stepping up your charity (effort or payments), to balance out the inevitable negative impact of the coming _Age of Bitcoin Inequality_.  ## Coming down from the ATH Even now, Bitcoin isn't the only safe asset; it's just the most-fungible and partitionable one, so that it's the one most akin to money. And lines are being blurred, as corporations, funds, governments, and insurers discharge dollars and stock up on harder reserve assets, including Bitcoin. They can hear the money printers rolling out, already, because nobody can print-n-spend, like Trump can. Let's not forget that the money for the last big bump came from the infamous Trump stimmy checks, that lots of us stacked on crypto.  As Bitcoin flows into such markets, the power will rest with both groups (the direct-hodlers and the title-holders), although the hodlers will initially have the upper hand. I say, _initially_ because many hodlers will need to discharge or invest Bitcoin, to live off of it, but the others don't need to, so it should eventually even out. It could take dozens or even hundreds of years to rebalance. By then, the world will be a very different place, and we don't know if Bitcoin will even still be a part of it. Assets come, assets go, and I'm just glad I didn't let down my forefathers, by leaving them with the first generation, who failed to adapt. Even if I'm a bit late, to the Bitcoin game, the ball is still in play. May the best money win. And may it be mine. And may I do good with it.
@ fd208ee8:0fd927c1
2024-11-07 07:28:06## The newspaper barons are all into crypto, now Watching the outsized-impact we crypto enthusiasts (I'm including Bitcoin in that category), had on the 2024 USA presidential election, was a sobering affair. At the moment, our impact is primarily over the voting box, but, already, indirectly, (over Elon Musik, Donald Trump, and Jack Dorsey, etc.) through our sheer wealth (and the ingenuity that brought us that wealth) being able to influence the voting population, by changing/shifting the communications channels and influencing what is written there. Elon even reached deep into his foreign-learned bag of political tricks and started [handing out money, directly](https://www.bbc.com/news/articles/crlnjzzk919o), to petition signers.  ## Survival of the fittest, ongoing Now, you all know that I have full respect for an expert player, when I see one, so no hating the hustle, from my side. We all play the hand we are dealt, and the political game is now such a pigsty, that you have to get a bit dirty, to have a chance at winning. Trying to stay neat and above the fray cost Republicans the last election.  It was the most dramatic display of the greatest power following the best money, that has been seen, since the Medici family began minting gold coins. The entire world is in shock. Change is upon us. He who has the best money, makes the rules. On a smaller, but not insignificant scale, private wealth and access to Bitcoin funding, have allowed quite a few of us Nostriches, to dedicate time and energy toward promoting and developing the New Internet. Whereas, other people's hobby is increasingly the night shift at the gas station, or doing something mind-numbing, to escape the realities of their current economic misery. You don't need money to be here, but you can spend more time here, if you have money. And we are here, writing the rules. We call them NIPs.  ## Same ole, same ole But back to us Bitcoiners... I increasingly don't see us morally any different than the clever people crowding into any safe asset, during any financial crisis. Like the people who bought agricultural land, gold, and Swiss Francs, before the Reichsmark melted down. The people who had that stuff, mostly managed to keep it, and their children and grandchildren have inherited it. Or they managed to marry back into families, that have done so, by remaining in the same social class, through beauty or talent.  We Bitcoiners have a good narrative to go along with our flight to economic safety, but everyone has that narrative. Humans have a conscience and need to justify their own actions, to themselves. I'm also a goldbug, you see, and a stockholder, and all three assets are rife with the same virtuous narrative. ## How do we save our financial behinds, without being evil? Some people are simply more situationally aware and have more agency, by nature and circumstances, and they adapt faster. It's not mere intelligence, rather, it also requires a willingness to act and take risks. There's an element of chance to it, but it's still always the same types of people ending up with the assets, with the winners slightly shifting with each round, due to evolution and changes in the environment. Charity was invented, to get such people to willingly share their assets, or the fruits of their assets, for the common good. So, rather than fret over the morality of the asset, itself, the better response is to consider stepping up your charity (effort or payments), to balance out the inevitable negative impact of the coming _Age of Bitcoin Inequality_.  ## Coming down from the ATH Even now, Bitcoin isn't the only safe asset; it's just the most-fungible and partitionable one, so that it's the one most akin to money. And lines are being blurred, as corporations, funds, governments, and insurers discharge dollars and stock up on harder reserve assets, including Bitcoin. They can hear the money printers rolling out, already, because nobody can print-n-spend, like Trump can. Let's not forget that the money for the last big bump came from the infamous Trump stimmy checks, that lots of us stacked on crypto.  As Bitcoin flows into such markets, the power will rest with both groups (the direct-hodlers and the title-holders), although the hodlers will initially have the upper hand. I say, _initially_ because many hodlers will need to discharge or invest Bitcoin, to live off of it, but the others don't need to, so it should eventually even out. It could take dozens or even hundreds of years to rebalance. By then, the world will be a very different place, and we don't know if Bitcoin will even still be a part of it. Assets come, assets go, and I'm just glad I didn't let down my forefathers, by leaving them with the first generation, who failed to adapt. Even if I'm a bit late, to the Bitcoin game, the ball is still in play. May the best money win. And may it be mine. And may I do good with it. @ fd208ee8:0fd927c1
2024-11-07 07:22:14## Unsucking the feed is real As a Nostrich with an interesting, thought-provoking, and informative feed... a feed so good, that we're creating clients just to look at that feed... a feed that puts a lie to the idea that Nostr is nothing, but people reposting from Twitter or rehashing worn-out Bitcoin memes... a feed that I personally and increasingly enjoy perusing... I am here to tell you that the feed is real.  It's taken me over a year, to produce this feed. I literally spent hours and hours, day in and day out, scouring the Nostrverse for people worth introducing other people to. It was brutally difficult, as I was fighting the inherent nature of the Nostr clients and relays, in their current, most-popular form. ## It goes like so... Here are the steps I took, that sometimes weren't possible to take, until I tried to take them, and that still will sometimes break your client because the clients are often _intentionally_ designed to steer you into having one particular feed: 1) **Make a screenshot** of your current relay list and copy your follows list. 2) **Unsubscribe from all the relays**, that you are currently subscribed to. Your feed should disappear. If it doesn't, or it doesn't allow for this, switch to a different client app because yours is corrupted. 3) **Unfollow everyone.** Delete the whole list. You are taking your follows private, which will invariably result in only following npubs whose stuff you actually want to see, since there's no longer any virtue-signaling going on. Also, it's easier to explain having no list, than a very short one. If your client doesn't allow for this, or starts throwing error messages and freezing up, then switch to a different client app because yours is corrupted. 4) **Curate your copied follows list.** Go line by line and look at the feed produced by the npub on that list. * Do you want to see that in your feed, going forward? * Do they produce original content and/or are they interesting conversationalists, in the replies? * Have they been active, within the past three months? * Are they simply good friends or real-life acquaintances, that you want to keep tabs on? * If not, cross out their name. * If you have been following someone because they repost or quote interesting things, **look at who they've been reposting** and follow them, instead. 5) Of the npubs remaining on your list, go through and select the 10 most interesting ones, and **look at the reposts and quotes** in their feed, and their topical lists like \"Favorites\", \"Devs\", \"Recipes\", etc. (Not their follows list, unless it's quite short, as follows tend to be full of people they follow for social-signaling or client-functional reasons, that they don't actively look at.) Find some new follows, there. 6) Now, set up a personal relay and add all the follows, that made the cut, to **your allowed-npubs list**. Do not add people to the list, just to make them feel better, or because you feel guilty, as they follow you, or to keep them from yelling at you. Remember, they can't see the list! 7) Think about the topics you find interesting, and add an **allowed-keywords list** (this is better than hashtags, as it searches the entire content of the notes), with the OR operator (these allowed npubs OR these allowed topics). 8) Make sure that you choose words likely to find the content you are most-interested in, and not people just ranting about it or spamming (those are great additions to your relay's block-list). If you are Muslim, for instance, instead of "Islam" or "shariah", choose "hadith" or "riba", as those are words more-likely to be used by people who know what they are talking about. If you are into bread baking, add "sourdough", "rye", "yeast", or "whisk", but don't add "bread" or "carbs". Once a note from those people shows up in your feed, and their feed looks like someone interesting, you can add their npub to your allow list. Remember: **The topics are there to find people to add to the allow list**, not merely for their own sake, as this is not a topical relay, but a personal one. 9) Open up a faucet (or relay syncing) with some of the big relays you previously unsubscribed from, some WoT relays, and some of the paid relays (nostr.land, nostr.wine, nostr21.com, and sovbit.host, for example). **Your relay will filter that feed** and only accept the events from the people and topics on your list. As your relay becomes more popular, npubs will begin writing directly to it, and the connections to other relays will sink in significance. 10) Go to your client of choice and **subscribe to your new relay**. Also subscribe to some topical relays, or curated neighborhood relays, you find interesting or your frens are running. This is an easy way to find new, interesting npubs, to add to your own relay.  That's a lot of work, you say? Yes, but the result is great, and you are now fully in-charge of your own feed. You also -- here's the cool part -- have a feed good enough, that other people can add your feed to theirs and enjoy your manual curation. As you refine and expand your feed, theirs will also be refined, in parallel. You are now an official Nostr Community Curator. My sincere congratulations.  ## Why is this so hard? This is only a lot of work because the clients aren't designed to interact with relays, to this extent, as they were created to service mega-relays, download all their crap to your local cache, and adjust the feed over the follows/mutes lists. This was an idea borne of the axiom that Relays Are Hard, so there will only ever be a handful of them, where we'd all clump together and the relay operators would never judge the quality of someone's content. Then, some unusually clever people made relays increasingly easy, and the mailbox communication model was invented, and here we are. What we have now, and that is slowly growing in popularity, among the #NostrIntelligentsia, are Nostr clients aimed at curating and viewing individual relays or personalized sets of smaller or more-specialized relays. The reigning client devs refused to give us those clients, and most of us aren't up to developing our own clients, so the relay devs took matters into their own hands and made the clients themselves. The free market remains undefeated. This is a total game-changer. Last one to board this train is a rotten egg. Originally, relays were supposed to be completely stupid and clients were supposed to be completely smart, but it's now actually the other way around, because most relay devs have a market-born incentive to make their content highly customizable and appealing to individuals (so that more people run relays). ## But what about algos? Can't you just slap an algo on top of Damus, Lol, or Primal relays, and get the same result? I would argue... no. No, you can't. Or, rather, only in the short to medium term. Running your own relay, is running your own server. You are now _intellectually independent_, at a machine-level, and therefore a fully sovereign consumer. If you then use algos to control your own server, or in a client that subscribes to your own server, then you can further-refine a feed that is already in a high-to-you-signal state, rather than risking an algo inching you toward the Consensus Feed. I have noticed that my own feed is slowly drifting away from the ReplyGuy-Cryptobot-Porny-Bitcoin-Meme Dumpster Fire, that almost everyone else is looking at, and it's due to running my own relay. If I use DVMs, those algos sometimes refer to relays I intentionally avoid, so they return results according to those relays. The results are as underwhelming, as you would expect, and often are simply 31 flavors of the Trending List. But, that isn't your problem, anymore. From here, you can actively expand and refine your feed, over your whitelist, the topics, and your personally-managed algos. Happy Nostr-ing!
@ fd208ee8:0fd927c1
2024-11-07 07:22:14## Unsucking the feed is real As a Nostrich with an interesting, thought-provoking, and informative feed... a feed so good, that we're creating clients just to look at that feed... a feed that puts a lie to the idea that Nostr is nothing, but people reposting from Twitter or rehashing worn-out Bitcoin memes... a feed that I personally and increasingly enjoy perusing... I am here to tell you that the feed is real.  It's taken me over a year, to produce this feed. I literally spent hours and hours, day in and day out, scouring the Nostrverse for people worth introducing other people to. It was brutally difficult, as I was fighting the inherent nature of the Nostr clients and relays, in their current, most-popular form. ## It goes like so... Here are the steps I took, that sometimes weren't possible to take, until I tried to take them, and that still will sometimes break your client because the clients are often _intentionally_ designed to steer you into having one particular feed: 1) **Make a screenshot** of your current relay list and copy your follows list. 2) **Unsubscribe from all the relays**, that you are currently subscribed to. Your feed should disappear. If it doesn't, or it doesn't allow for this, switch to a different client app because yours is corrupted. 3) **Unfollow everyone.** Delete the whole list. You are taking your follows private, which will invariably result in only following npubs whose stuff you actually want to see, since there's no longer any virtue-signaling going on. Also, it's easier to explain having no list, than a very short one. If your client doesn't allow for this, or starts throwing error messages and freezing up, then switch to a different client app because yours is corrupted. 4) **Curate your copied follows list.** Go line by line and look at the feed produced by the npub on that list. * Do you want to see that in your feed, going forward? * Do they produce original content and/or are they interesting conversationalists, in the replies? * Have they been active, within the past three months? * Are they simply good friends or real-life acquaintances, that you want to keep tabs on? * If not, cross out their name. * If you have been following someone because they repost or quote interesting things, **look at who they've been reposting** and follow them, instead. 5) Of the npubs remaining on your list, go through and select the 10 most interesting ones, and **look at the reposts and quotes** in their feed, and their topical lists like \"Favorites\", \"Devs\", \"Recipes\", etc. (Not their follows list, unless it's quite short, as follows tend to be full of people they follow for social-signaling or client-functional reasons, that they don't actively look at.) Find some new follows, there. 6) Now, set up a personal relay and add all the follows, that made the cut, to **your allowed-npubs list**. Do not add people to the list, just to make them feel better, or because you feel guilty, as they follow you, or to keep them from yelling at you. Remember, they can't see the list! 7) Think about the topics you find interesting, and add an **allowed-keywords list** (this is better than hashtags, as it searches the entire content of the notes), with the OR operator (these allowed npubs OR these allowed topics). 8) Make sure that you choose words likely to find the content you are most-interested in, and not people just ranting about it or spamming (those are great additions to your relay's block-list). If you are Muslim, for instance, instead of "Islam" or "shariah", choose "hadith" or "riba", as those are words more-likely to be used by people who know what they are talking about. If you are into bread baking, add "sourdough", "rye", "yeast", or "whisk", but don't add "bread" or "carbs". Once a note from those people shows up in your feed, and their feed looks like someone interesting, you can add their npub to your allow list. Remember: **The topics are there to find people to add to the allow list**, not merely for their own sake, as this is not a topical relay, but a personal one. 9) Open up a faucet (or relay syncing) with some of the big relays you previously unsubscribed from, some WoT relays, and some of the paid relays (nostr.land, nostr.wine, nostr21.com, and sovbit.host, for example). **Your relay will filter that feed** and only accept the events from the people and topics on your list. As your relay becomes more popular, npubs will begin writing directly to it, and the connections to other relays will sink in significance. 10) Go to your client of choice and **subscribe to your new relay**. Also subscribe to some topical relays, or curated neighborhood relays, you find interesting or your frens are running. This is an easy way to find new, interesting npubs, to add to your own relay.  That's a lot of work, you say? Yes, but the result is great, and you are now fully in-charge of your own feed. You also -- here's the cool part -- have a feed good enough, that other people can add your feed to theirs and enjoy your manual curation. As you refine and expand your feed, theirs will also be refined, in parallel. You are now an official Nostr Community Curator. My sincere congratulations.  ## Why is this so hard? This is only a lot of work because the clients aren't designed to interact with relays, to this extent, as they were created to service mega-relays, download all their crap to your local cache, and adjust the feed over the follows/mutes lists. This was an idea borne of the axiom that Relays Are Hard, so there will only ever be a handful of them, where we'd all clump together and the relay operators would never judge the quality of someone's content. Then, some unusually clever people made relays increasingly easy, and the mailbox communication model was invented, and here we are. What we have now, and that is slowly growing in popularity, among the #NostrIntelligentsia, are Nostr clients aimed at curating and viewing individual relays or personalized sets of smaller or more-specialized relays. The reigning client devs refused to give us those clients, and most of us aren't up to developing our own clients, so the relay devs took matters into their own hands and made the clients themselves. The free market remains undefeated. This is a total game-changer. Last one to board this train is a rotten egg. Originally, relays were supposed to be completely stupid and clients were supposed to be completely smart, but it's now actually the other way around, because most relay devs have a market-born incentive to make their content highly customizable and appealing to individuals (so that more people run relays). ## But what about algos? Can't you just slap an algo on top of Damus, Lol, or Primal relays, and get the same result? I would argue... no. No, you can't. Or, rather, only in the short to medium term. Running your own relay, is running your own server. You are now _intellectually independent_, at a machine-level, and therefore a fully sovereign consumer. If you then use algos to control your own server, or in a client that subscribes to your own server, then you can further-refine a feed that is already in a high-to-you-signal state, rather than risking an algo inching you toward the Consensus Feed. I have noticed that my own feed is slowly drifting away from the ReplyGuy-Cryptobot-Porny-Bitcoin-Meme Dumpster Fire, that almost everyone else is looking at, and it's due to running my own relay. If I use DVMs, those algos sometimes refer to relays I intentionally avoid, so they return results according to those relays. The results are as underwhelming, as you would expect, and often are simply 31 flavors of the Trending List. But, that isn't your problem, anymore. From here, you can actively expand and refine your feed, over your whitelist, the topics, and your personally-managed algos. Happy Nostr-ing! @ f462d21e:1390b6b1
2024-11-07 03:52:04eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyIsImZlZWRiYWNrIjp7ImZlZWRiYWNrIjowLCJwYWdlciI6eyJ0b3RhbEl0ZW1zIjowfSwibWVzc2FnZSI6Im5vIHJlc3VsdHMgZm91bmQifX0=
@ f462d21e:1390b6b1
2024-11-07 03:52:04eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyIsImZlZWRiYWNrIjp7ImZlZWRiYWNrIjowLCJwYWdlciI6eyJ0b3RhbEl0ZW1zIjowfSwibWVzc2FnZSI6Im5vIHJlc3VsdHMgZm91bmQifX0= @ f462d21e:1390b6b1
2024-11-06 04:39:14eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9
@ f462d21e:1390b6b1
2024-11-06 04:39:14eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9 @ f462d21e:1390b6b1
2024-11-06 04:19:42eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9
@ f462d21e:1390b6b1
2024-11-06 04:19:42eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9 @ f462d21e:1390b6b1
2024-11-06 04:14:05eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9
@ f462d21e:1390b6b1
2024-11-06 04:14:05eyJfaWQiOiI2Njk1ZmZjZDUyYTMzYTg2YTMxOGUxYzAiLCJ1c2VybmFtZSI6ImtoYWxlZCIsImZlZWRiYWNrU2NvcmUiOjAsImNyZWF0ZWRfb24iOiIyMDI0LTA3LTE2VDA1OjA2OjIxLjA0OFoiLCJ0cmFkZXMiOjEsInRyYWRpbmdQYXJ0bmVycyI6MSwicHVibGljS2V5IjoiZGI0MzViZjAzYzU4Zjk4NTEwMzZiODZkYjI4OGIxMTJkYWRkYzAzMjc5ZTQ0MzkzOTY2MzkzYzE0MDQ3OWEwYyJ9 @ a367f9eb:0633efea
2024-11-05 08:48:41Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application. The [reporting](https://www.reuters.com/technology/artificial-intelligence/chinese-researchers-develop-ai-model-military-use-back-metas-llama-2024-11-01/) purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States. > In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”. > > The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making. While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place. Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran? The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer. With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line. Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history? As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times. At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative. Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this. Open-source matters When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it. The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made. While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit. Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers. Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other. I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run. Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots). This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money. You know what else is open-source and available for everyone to use, modify, and build upon? PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit. Open-source code is speech, and it is knowledge. We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge. Open-source is for your friends, and enemies In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license. At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth). Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created. We know this can be useful to friends, but what about enemies? As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications. The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians. A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software. If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then. Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to. Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place. Limiting open-source threatens our own advancement If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way. If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible. The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols. The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing. But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source. If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries. Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application. The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States. > In a June paper reviewed by[ Reuters](https://www.reuters.com/technology/artificial-intelligence/chinese-researchers-develop-ai-model-military-use-back-metas-llama-2024-11-01/), six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”. > > The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making. While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the *Star Trek* episode “[A Taste of Armageddon](https://en.wikipedia.org/wiki/A_Taste_of_Armageddon)“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place. Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran? The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over [one million open-source LLMs](https://huggingface.co/models) available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer. With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are [potentially](https://bigthink.com/business/the-trillion-dollar-ai-race-to-create-digital-god/) trillions of dollars on the line. Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American[ infrastructure](https://www.nbcnews.com/tech/security/chinese-hackers-cisa-cyber-5-years-us-infrastructure-attack-rcna137706),[ data](https://www.cnn.com/2024/10/05/politics/chinese-hackers-us-telecoms/index.html), and yes, [your credit history](https://thespectator.com/topic/chinese-communist-party-credit-history-equifax/)? **As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much[ many times](https://consumerchoicecenter.org/made-in-china-sold-in-china/).** At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative. Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this. ## **Open-source matters** When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it. The various [licensing schemes](https://opensource.org/licenses) – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made. While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit. Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers. Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other. I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run. Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots). This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also [open-source](https://github.com/bitcoin), which has allowed [thousands](https://bitcoinmagazine.com/business/bitcoin-is-money-for-enemies) of copycat protocols that have revolutionized how we view money. You know what else is open-source and available for everyone to use, modify, and build upon? PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit. Open-source code is speech, and it is knowledge. We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge. ## **Open-source is for your friends, and enemies** In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license. At this very moment, you can click on over to[ Hugging Face](https://huggingface.co/), download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth). Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created. We know this can be useful to friends, but what about enemies? As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications. The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians. A bipartisan group of US House lawmakers want to put [export controls](https://www.reuters.com/technology/us-lawmakers-unveil-bill-make-it-easier-restrict-exports-ai-models-2024-05-10/) on AI models, as well as block foreign access to US cloud servers that may be hosting AI software. If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see[ The Crypto Wars](https://en.wikipedia.org/wiki/Export_of_cryptography_from_the_United_States)). Many of the arguments we hear today were invoked by some of the same people as back then. Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to. Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place. ## **Limiting open-source threatens our own advancement** If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way. If there is a “[Hundred Year Marathon](https://www.amazon.com/Hundred-Year-Marathon-Strategy-Replace-Superpower/dp/1250081343)” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible. The Chinese military has been building up its capabilities with [trillions of dollars’](https://www.economist.com/china/2024/11/04/in-some-areas-of-military-strength-china-has-surpassed-america) worth of investments that span far beyond AI chatbots and skip logic protocols. The [theft](https://www.technologyreview.com/2023/06/20/1075088/chinese-amazon-seller-counterfeit-lawsuit/) of intellectual property at factories in Shenzhen, or in US courts by [third-party litigation funding](https://nationalinterest.org/blog/techland/litigation-finance-exposes-our-judicial-system-foreign-exploitation-210207) coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing. But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source. If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries. *Originally published on the website of the [Consumer Choice Center](https://consumerchoicecenter.org/open-source-is-for-everyone-even-your-adversaries/).*
@ a367f9eb:0633efea
2024-11-05 08:48:41Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application. The [reporting](https://www.reuters.com/technology/artificial-intelligence/chinese-researchers-develop-ai-model-military-use-back-metas-llama-2024-11-01/) purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States. > In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”. > > The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making. While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place. Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran? The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer. With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line. Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history? As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times. At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative. Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this. Open-source matters When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it. The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made. While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit. Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers. Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other. I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run. Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots). This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money. You know what else is open-source and available for everyone to use, modify, and build upon? PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit. Open-source code is speech, and it is knowledge. We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge. Open-source is for your friends, and enemies In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license. At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth). Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created. We know this can be useful to friends, but what about enemies? As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications. The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians. A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software. If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then. Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to. Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place. Limiting open-source threatens our own advancement If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way. If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible. The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols. The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing. But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source. If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries. Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application. The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States. > In a June paper reviewed by[ Reuters](https://www.reuters.com/technology/artificial-intelligence/chinese-researchers-develop-ai-model-military-use-back-metas-llama-2024-11-01/), six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”. > > The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making. While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the *Star Trek* episode “[A Taste of Armageddon](https://en.wikipedia.org/wiki/A_Taste_of_Armageddon)“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place. Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran? The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over [one million open-source LLMs](https://huggingface.co/models) available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer. With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are [potentially](https://bigthink.com/business/the-trillion-dollar-ai-race-to-create-digital-god/) trillions of dollars on the line. Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American[ infrastructure](https://www.nbcnews.com/tech/security/chinese-hackers-cisa-cyber-5-years-us-infrastructure-attack-rcna137706),[ data](https://www.cnn.com/2024/10/05/politics/chinese-hackers-us-telecoms/index.html), and yes, [your credit history](https://thespectator.com/topic/chinese-communist-party-credit-history-equifax/)? **As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much[ many times](https://consumerchoicecenter.org/made-in-china-sold-in-china/).** At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative. Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this. ## **Open-source matters** When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it. The various [licensing schemes](https://opensource.org/licenses) – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made. While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit. Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers. Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other. I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run. Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots). This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also [open-source](https://github.com/bitcoin), which has allowed [thousands](https://bitcoinmagazine.com/business/bitcoin-is-money-for-enemies) of copycat protocols that have revolutionized how we view money. You know what else is open-source and available for everyone to use, modify, and build upon? PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit. Open-source code is speech, and it is knowledge. We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge. ## **Open-source is for your friends, and enemies** In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license. At this very moment, you can click on over to[ Hugging Face](https://huggingface.co/), download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth). Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created. We know this can be useful to friends, but what about enemies? As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications. The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians. A bipartisan group of US House lawmakers want to put [export controls](https://www.reuters.com/technology/us-lawmakers-unveil-bill-make-it-easier-restrict-exports-ai-models-2024-05-10/) on AI models, as well as block foreign access to US cloud servers that may be hosting AI software. If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see[ The Crypto Wars](https://en.wikipedia.org/wiki/Export_of_cryptography_from_the_United_States)). Many of the arguments we hear today were invoked by some of the same people as back then. Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to. Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place. ## **Limiting open-source threatens our own advancement** If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way. If there is a “[Hundred Year Marathon](https://www.amazon.com/Hundred-Year-Marathon-Strategy-Replace-Superpower/dp/1250081343)” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible. The Chinese military has been building up its capabilities with [trillions of dollars’](https://www.economist.com/china/2024/11/04/in-some-areas-of-military-strength-china-has-surpassed-america) worth of investments that span far beyond AI chatbots and skip logic protocols. The [theft](https://www.technologyreview.com/2023/06/20/1075088/chinese-amazon-seller-counterfeit-lawsuit/) of intellectual property at factories in Shenzhen, or in US courts by [third-party litigation funding](https://nationalinterest.org/blog/techland/litigation-finance-exposes-our-judicial-system-foreign-exploitation-210207) coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing. But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source. If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries. *Originally published on the website of the [Consumer Choice Center](https://consumerchoicecenter.org/open-source-is-for-everyone-even-your-adversaries/).* @ a10260a2:caa23e3e
2024-11-05 06:21:10TIL Google Authenticator can potentially collect a lot of data, more than some of the other popular 2FA apps[^1]. [^1]: https://www.pcmag.com/reviews/google-authenticator 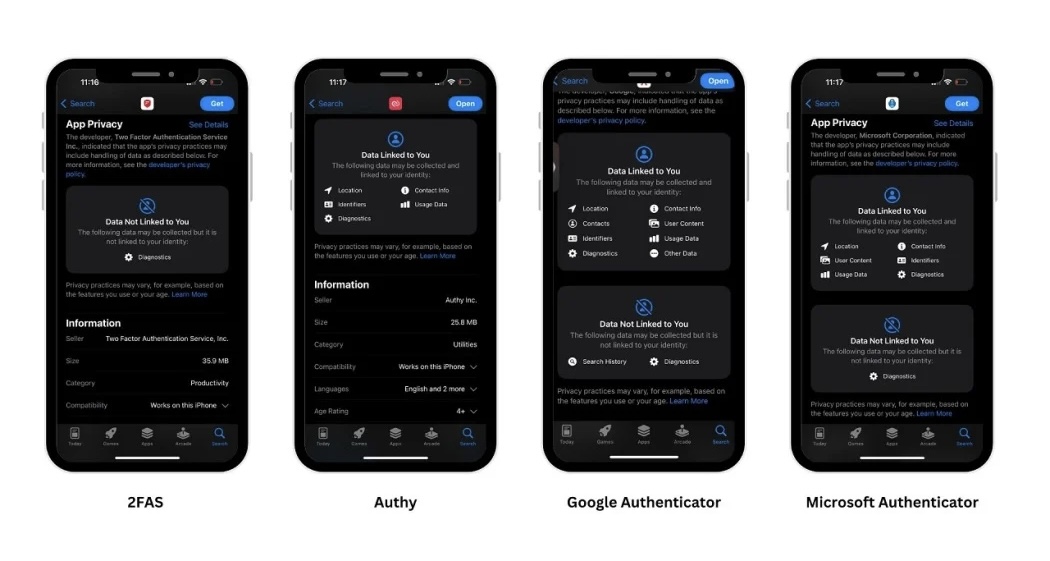 Whether it does or it doesn’t, if you’re like me, you don’t turn down an opportunity to remove some Google from your life and add in some open-source. Here’s a quick overview of the migration process. **Step 1: Download [2FAS](https://apps.apple.com/us/app/2fa-authenticator-2fas/id1217793794)**  **Step 2: Export accounts from Authenticator** This can be done via “Transfer accounts” in the sidebar. If you’re transferring on the same phone, take a screenshot of the QR code.  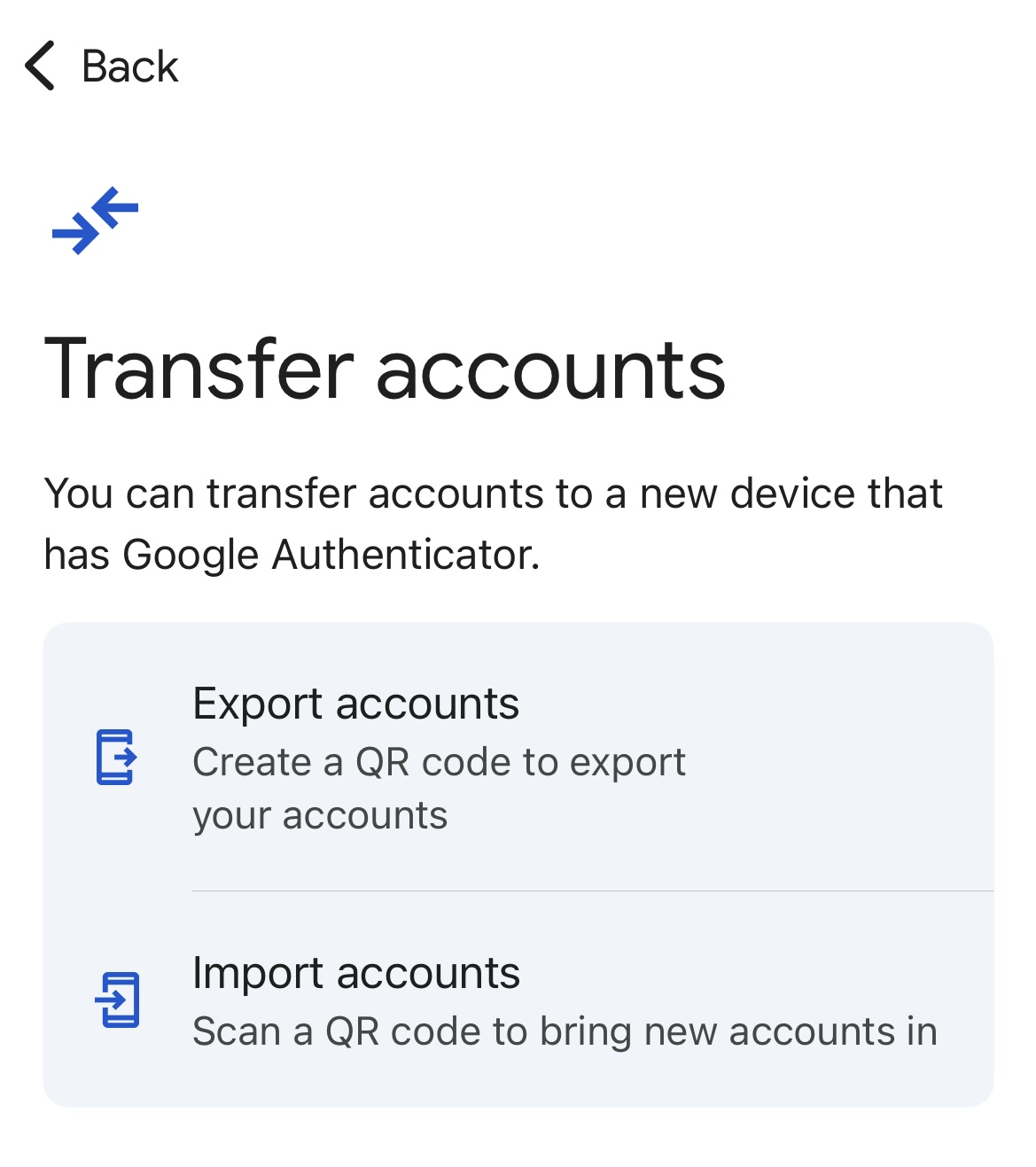 **Step 3: Import accounts into 2FAS** During the setup process for 2FAS, you’ll be given the option to import existing tokens from Google. This is where you’ll tap “Choose QR Code” and select the screenshot you took in step 2. 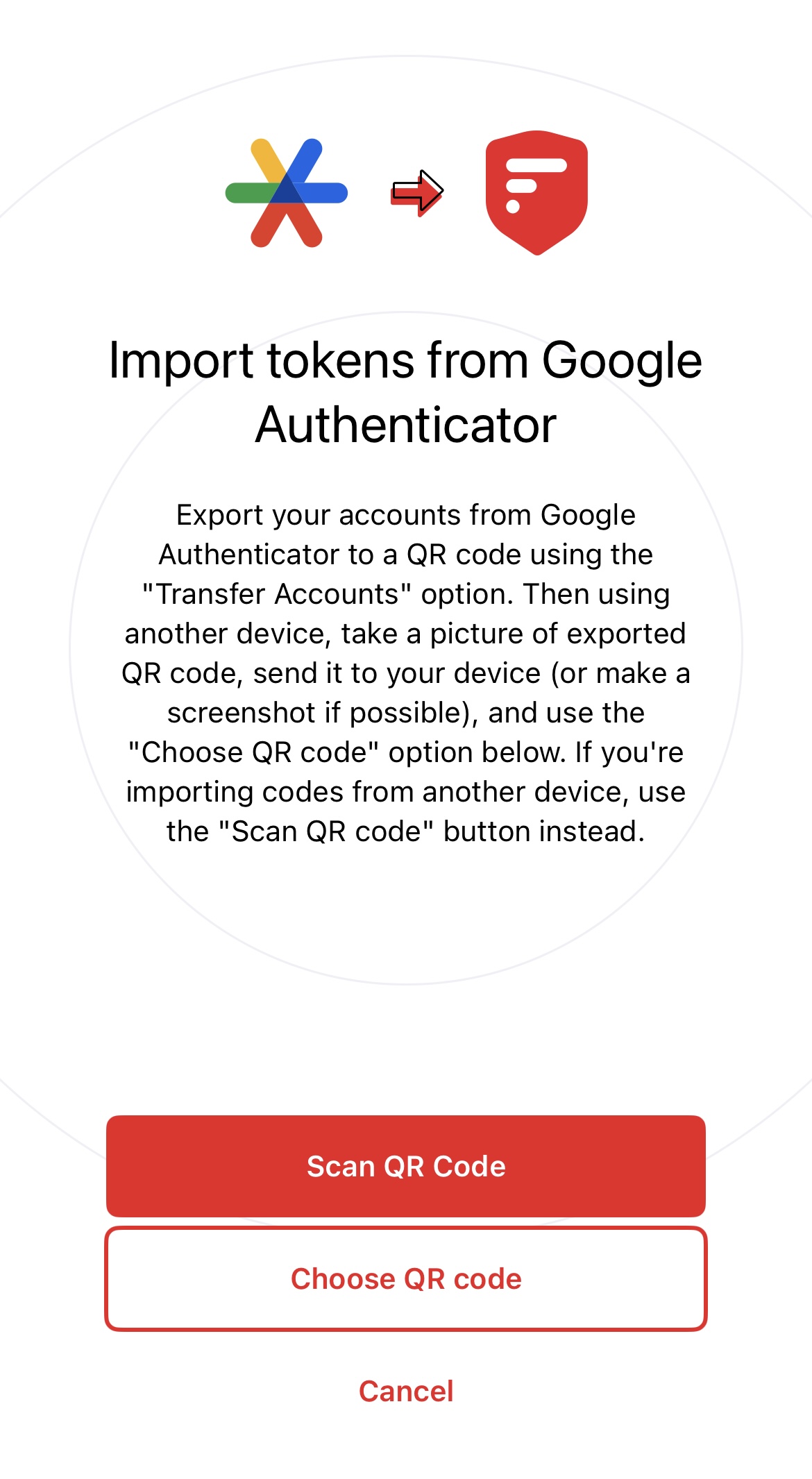 Note that when you tap continue after importing the tokens, you’ll be taken back to the same screen as above. I think it should take you to your list of accounts after. Either way, don’t think the import failed. Just tap cancel, and you’ll be taken there. 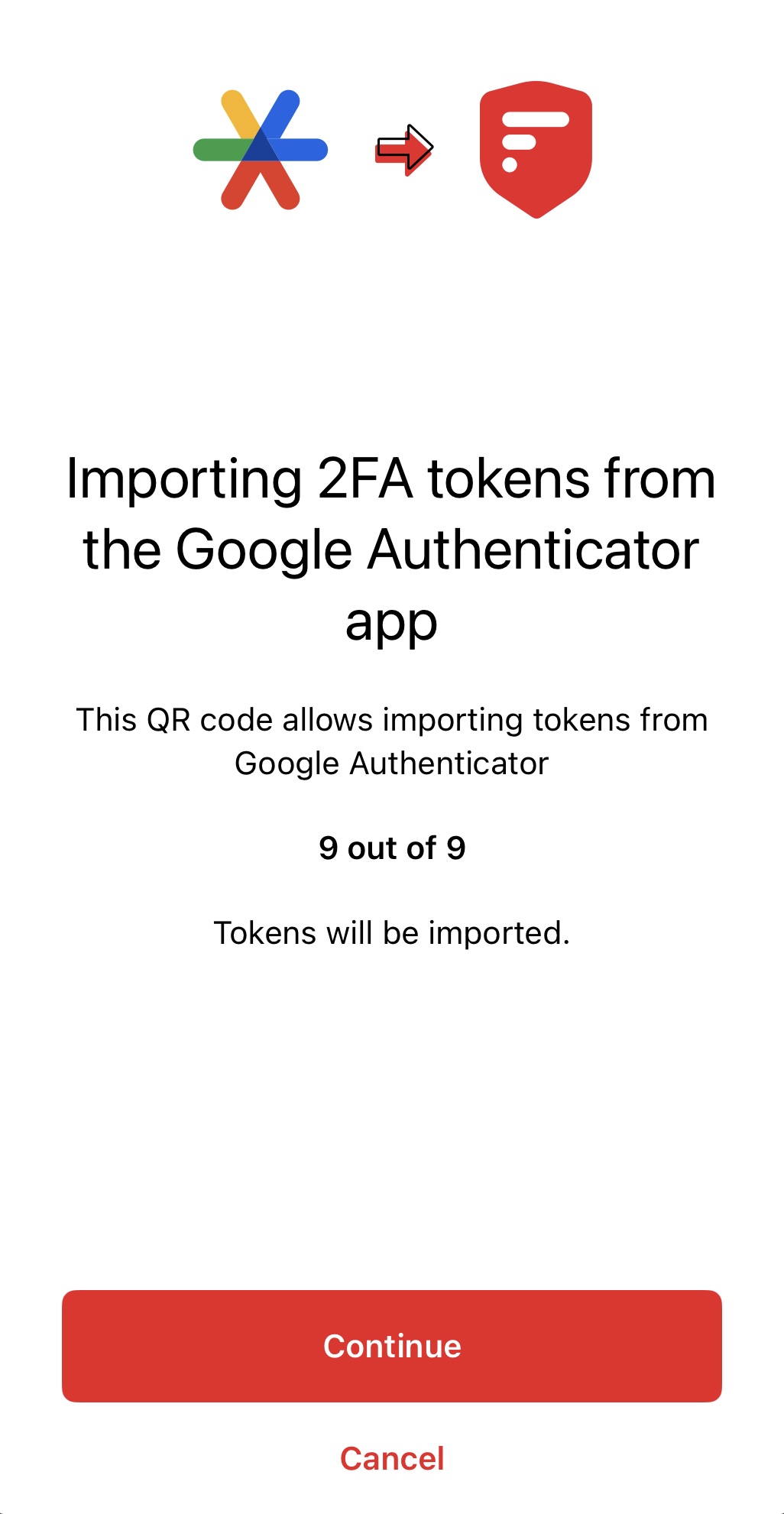 If you’re on Android, check out [Aegis](https://github.com/beemdevelopment/Aegis). 🫡 originally posted at https://stacker.news/items/753472
@ a10260a2:caa23e3e
2024-11-05 06:21:10TIL Google Authenticator can potentially collect a lot of data, more than some of the other popular 2FA apps[^1]. [^1]: https://www.pcmag.com/reviews/google-authenticator 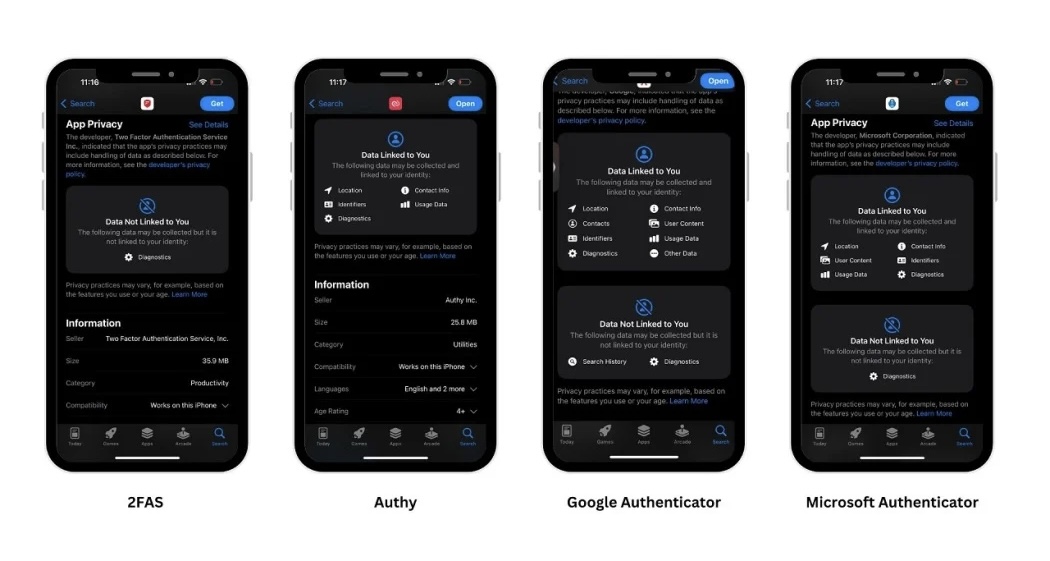 Whether it does or it doesn’t, if you’re like me, you don’t turn down an opportunity to remove some Google from your life and add in some open-source. Here’s a quick overview of the migration process. **Step 1: Download [2FAS](https://apps.apple.com/us/app/2fa-authenticator-2fas/id1217793794)**  **Step 2: Export accounts from Authenticator** This can be done via “Transfer accounts” in the sidebar. If you’re transferring on the same phone, take a screenshot of the QR code.   **Step 3: Import accounts into 2FAS** During the setup process for 2FAS, you’ll be given the option to import existing tokens from Google. This is where you’ll tap “Choose QR Code” and select the screenshot you took in step 2. 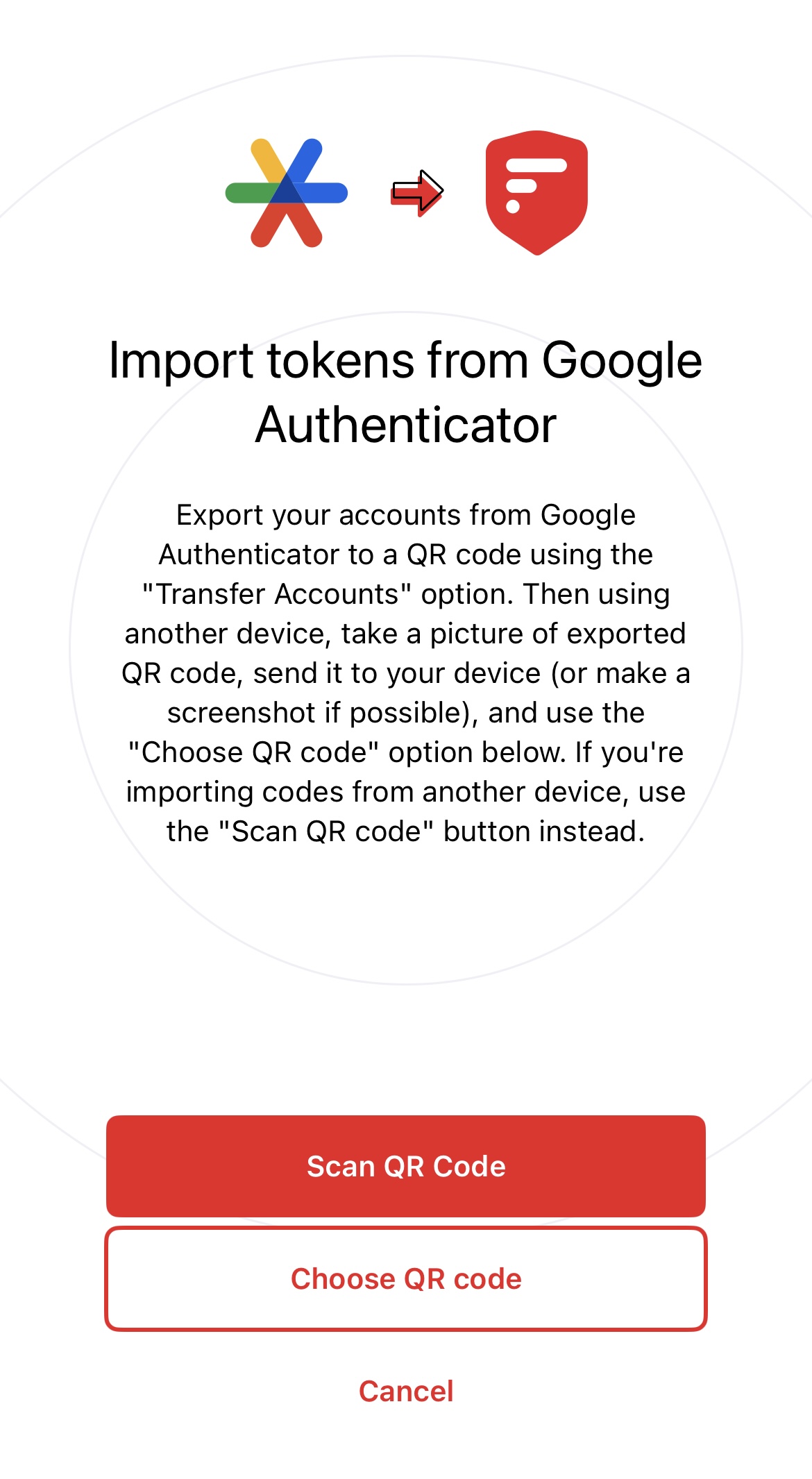 Note that when you tap continue after importing the tokens, you’ll be taken back to the same screen as above. I think it should take you to your list of accounts after. Either way, don’t think the import failed. Just tap cancel, and you’ll be taken there. 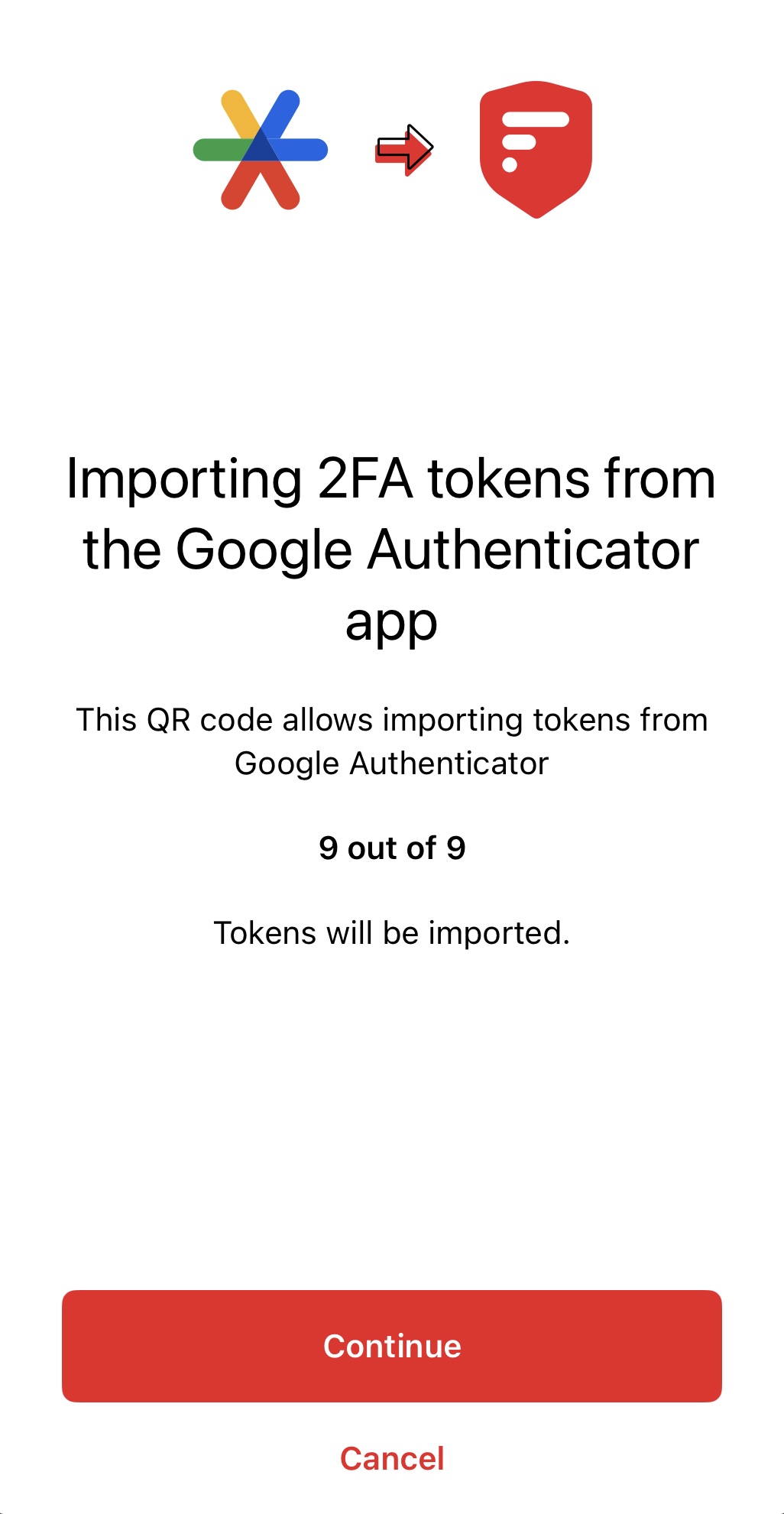 If you’re on Android, check out [Aegis](https://github.com/beemdevelopment/Aegis). 🫡 originally posted at https://stacker.news/items/753472 @ 472f440f:5669301e
2024-11-05 04:24:47All eyes are, unsurprisingly, on the US Presidential election. Tomorrow is the big day. I don't want to come off as preachy, however it is pretty clear to me that if you are an American citizen who cares about bitcoin and would like to live under an administration that is eager to embrace the industry as opposed to an administration that is actively hostile toward bitcoin there is only one candidate who deserves your vote; Donald J. Trump. I think he's a better candidate for other reasons, but if you've read this rag for long enough you probably already know what those are. Instead of writing a screed about why I am voting for Trump, let's highlight some things outside of the election that you should be paying attention to this week. First up, there are two Treasury auctions; $42B of 10-Year notes tomorrow and $25B 30-Year bonds on Wednesday. It will be interesting to see what the demand for these auctions is and how they affect rates. The long end of the yield curve has been pumping since the Fed's rate cut in the middle of September, which is the market signaling that it does not believe inflation has been appropriately tamed. Yields came down today, but as you can see from the charts things are trending in the wrong direction. As the Treasury issues new debt at higher rates, the interest expense on that debt, naturally, drifts higher. If the long end of the yield curve doesn't come down aggressively over the course of the next year this is going to be a big problem. There are trillions of dollars worth of Treasury debt that needs the be rolled over in the next few years and it would be advantageous for the Treasury if that debt wasn't being rolled over with yields as high as they are. With the amount of debt the country has accrued in recent decades, every incremental dollar of debt that gets issued and/or rolled over at higher interest rates exacerbates the problem. We are approaching the territory of runaway exponentials, as evidenced by this chart. The growth slope gets steeper and steeper This debt problem is the elephant in the room that needs to be addressed as quickly as possible. The national debt hit $1.2T in early 1983. It then took 26 years to 10x from $1.2T to $12T in late 2009 and has only taken another 15 years to triple from there to $36T or 30x from the arbitrary base I picked out (Q1 1983). With this in mind, keep an eye out for these auctions tomorrow and Wednesday, where rates end at the end of trading on Wednesday, and whether or not we officially push over $36T. Regardless of who wins the election tomorrow, this is a problem that needs to be confronted. Whether or not it can be solved at all is up for debate. I don't see how what can be done to reel in this runaway train at this point. However, at the very least, we should acknowledge that we're in the realm of exponentials and have people prepare accordingly by accumulating hard assets that cannot be debased (bitcoin). The other thing to pay attention to is the FOMC meeting on Wednesday and the announcement of the results of the meeting on Thursday. Will Jerome and the other Fed board members to keep rates where they are, cut, or raise rates? Raising rates seems to be out of the question despite the fact that many believe it would be the most prudent move considering how the long end of the yield curve reacted to the 50bps cut in September. If they decide to cut rates, by how much will they cut them? Will they slow the pace with a 25bps cut or continue at the 50bps clip established in September? We'll find toward the end of this week. Don't lose sight of these events while the world is enthralled with the elections in the US. I don't know about you freaks, but I couldn't feel more fortunate that bitcoin exists at a time like this. Having access to a distributed peer-to-peer digital cash system with a fixed supply during a time of incredible political divisiveness and out-of-control runaway sovereign debt feels like a Godsend. Stay sane out there. Final thought... We're going to win.
@ 472f440f:5669301e
2024-11-05 04:24:47All eyes are, unsurprisingly, on the US Presidential election. Tomorrow is the big day. I don't want to come off as preachy, however it is pretty clear to me that if you are an American citizen who cares about bitcoin and would like to live under an administration that is eager to embrace the industry as opposed to an administration that is actively hostile toward bitcoin there is only one candidate who deserves your vote; Donald J. Trump. I think he's a better candidate for other reasons, but if you've read this rag for long enough you probably already know what those are. Instead of writing a screed about why I am voting for Trump, let's highlight some things outside of the election that you should be paying attention to this week. First up, there are two Treasury auctions; $42B of 10-Year notes tomorrow and $25B 30-Year bonds on Wednesday. It will be interesting to see what the demand for these auctions is and how they affect rates. The long end of the yield curve has been pumping since the Fed's rate cut in the middle of September, which is the market signaling that it does not believe inflation has been appropriately tamed. Yields came down today, but as you can see from the charts things are trending in the wrong direction. As the Treasury issues new debt at higher rates, the interest expense on that debt, naturally, drifts higher. If the long end of the yield curve doesn't come down aggressively over the course of the next year this is going to be a big problem. There are trillions of dollars worth of Treasury debt that needs the be rolled over in the next few years and it would be advantageous for the Treasury if that debt wasn't being rolled over with yields as high as they are. With the amount of debt the country has accrued in recent decades, every incremental dollar of debt that gets issued and/or rolled over at higher interest rates exacerbates the problem. We are approaching the territory of runaway exponentials, as evidenced by this chart. The growth slope gets steeper and steeper This debt problem is the elephant in the room that needs to be addressed as quickly as possible. The national debt hit $1.2T in early 1983. It then took 26 years to 10x from $1.2T to $12T in late 2009 and has only taken another 15 years to triple from there to $36T or 30x from the arbitrary base I picked out (Q1 1983). With this in mind, keep an eye out for these auctions tomorrow and Wednesday, where rates end at the end of trading on Wednesday, and whether or not we officially push over $36T. Regardless of who wins the election tomorrow, this is a problem that needs to be confronted. Whether or not it can be solved at all is up for debate. I don't see how what can be done to reel in this runaway train at this point. However, at the very least, we should acknowledge that we're in the realm of exponentials and have people prepare accordingly by accumulating hard assets that cannot be debased (bitcoin). The other thing to pay attention to is the FOMC meeting on Wednesday and the announcement of the results of the meeting on Thursday. Will Jerome and the other Fed board members to keep rates where they are, cut, or raise rates? Raising rates seems to be out of the question despite the fact that many believe it would be the most prudent move considering how the long end of the yield curve reacted to the 50bps cut in September. If they decide to cut rates, by how much will they cut them? Will they slow the pace with a 25bps cut or continue at the 50bps clip established in September? We'll find toward the end of this week. Don't lose sight of these events while the world is enthralled with the elections in the US. I don't know about you freaks, but I couldn't feel more fortunate that bitcoin exists at a time like this. Having access to a distributed peer-to-peer digital cash system with a fixed supply during a time of incredible political divisiveness and out-of-control runaway sovereign debt feels like a Godsend. Stay sane out there. Final thought... We're going to win. @ fd208ee8:0fd927c1
2024-11-03 21:51:39## All memed out It finally happened. I think it was October 25th, at circa 18:45 in the evening. I was doomscrolling my Nostr feed, and kept seeing the same Bitcoin memes repeated over and over, by different people. They weren't even reposts, they were copy-pasted versions of the same image. A very funny image. Well, it was very funny last year... and the year before that... and probably the year before that, when it appeared on a different network. Because it's all just reposts, copy-pastes and rehashes of the Best of Bitcoin Twitter, just like the tiresome influencers, with their groupies and their Episode 498 of *Let's all eat a large chunk of lightly-burnt dead animal and count our stacks before jetting off to talk about how to save the poors by getting them to buy individual satoshis with money they don't have*.  ## I'm the poors your looking for It's all so tiresome. It has little bearing on the real world I see around me, where most people are thinking all day about 99 problems and Bitcoin ain't one.  Which is, of course, what the Bitcoin influencers would have you believe, is the reason that they're poor. What in the world could be more important, than thinking about Bitcoin? Why do these people not get with the program? Don't they know, that we are trying to save them?  Why are they worrying about OtherProblems? Don't they know that all OtherProblems can be fixed with Bitcoin? Really, if you just go back far enough, in any current, situational problem, you will discover that there was some slight, negative shift to the history record that involved soft money. It's the financial version of the Butterfly Effect.  That's why #BitcoinFixesThis. Bitcoin fixes everything, if you just think about it, for long enough. The same way that we all actually come out of Africa, supposedly, if you go back enough generations. So, coming out of Africa, now, as a Real Life Person in The Present is supposed to have no significance. What does someone from Cameroon know about Africa, that someone from Alaska doesn't? Both people come out of Africa, if you just think about it, for long enough.  And maybe that really is true. Maybe Bitcoin will eventually end all vice and crimes, save the planet, and we will all just hold hands and sing kumbaya all day, while waiting for the Singularity to upload us to Satoshi. ## Bitcoin envelope budgeting Or maybe it's not. Maybe it's just a really hard, digital money that incentivizes savings, functions as a reliable measure, and makes micropayments possible on a global scale. Those really are things that will help the poors, including myself. I can see it, already, when trying to organize pre-paid meetups or figure out what to do with our household's meager savings, when the stock market is looking particularly bubblicious.  But this is what I would consider Boring Bitcoin. Bitcoin home economics. Penny-pinching Bitcoin. Bitcoin for homemakers. How to use the Bitcoin envelope budgeting system to beat inflation by a margin of 13%. The actual use of Bitcoin as money, rather than as a mere investment gamble or hype machine. That's the part of Bitcoin that nobody seems to really talk about because it's incredibly practical, dull, and useful, and it can only be tested by -- Oh, the horror! -- actually spending Bitcoin. But... perhaps I will begin talking about it. Perhaps those of us, Bitcoiners, who are having fun staying poor, while stacking sats, should speak up a bit more. Perhaps the boring stuff is actually the interesting stuff. Perhaps there is more to say about Bitcoin, than can fit into a meme.
@ fd208ee8:0fd927c1
2024-11-03 21:51:39## All memed out It finally happened. I think it was October 25th, at circa 18:45 in the evening. I was doomscrolling my Nostr feed, and kept seeing the same Bitcoin memes repeated over and over, by different people. They weren't even reposts, they were copy-pasted versions of the same image. A very funny image. Well, it was very funny last year... and the year before that... and probably the year before that, when it appeared on a different network. Because it's all just reposts, copy-pastes and rehashes of the Best of Bitcoin Twitter, just like the tiresome influencers, with their groupies and their Episode 498 of *Let's all eat a large chunk of lightly-burnt dead animal and count our stacks before jetting off to talk about how to save the poors by getting them to buy individual satoshis with money they don't have*.  ## I'm the poors your looking for It's all so tiresome. It has little bearing on the real world I see around me, where most people are thinking all day about 99 problems and Bitcoin ain't one.  Which is, of course, what the Bitcoin influencers would have you believe, is the reason that they're poor. What in the world could be more important, than thinking about Bitcoin? Why do these people not get with the program? Don't they know, that we are trying to save them?  Why are they worrying about OtherProblems? Don't they know that all OtherProblems can be fixed with Bitcoin? Really, if you just go back far enough, in any current, situational problem, you will discover that there was some slight, negative shift to the history record that involved soft money. It's the financial version of the Butterfly Effect.  That's why #BitcoinFixesThis. Bitcoin fixes everything, if you just think about it, for long enough. The same way that we all actually come out of Africa, supposedly, if you go back enough generations. So, coming out of Africa, now, as a Real Life Person in The Present is supposed to have no significance. What does someone from Cameroon know about Africa, that someone from Alaska doesn't? Both people come out of Africa, if you just think about it, for long enough.  And maybe that really is true. Maybe Bitcoin will eventually end all vice and crimes, save the planet, and we will all just hold hands and sing kumbaya all day, while waiting for the Singularity to upload us to Satoshi. ## Bitcoin envelope budgeting Or maybe it's not. Maybe it's just a really hard, digital money that incentivizes savings, functions as a reliable measure, and makes micropayments possible on a global scale. Those really are things that will help the poors, including myself. I can see it, already, when trying to organize pre-paid meetups or figure out what to do with our household's meager savings, when the stock market is looking particularly bubblicious.  But this is what I would consider Boring Bitcoin. Bitcoin home economics. Penny-pinching Bitcoin. Bitcoin for homemakers. How to use the Bitcoin envelope budgeting system to beat inflation by a margin of 13%. The actual use of Bitcoin as money, rather than as a mere investment gamble or hype machine. That's the part of Bitcoin that nobody seems to really talk about because it's incredibly practical, dull, and useful, and it can only be tested by -- Oh, the horror! -- actually spending Bitcoin. But... perhaps I will begin talking about it. Perhaps those of us, Bitcoiners, who are having fun staying poor, while stacking sats, should speak up a bit more. Perhaps the boring stuff is actually the interesting stuff. Perhaps there is more to say about Bitcoin, than can fit into a meme. @ fd208ee8:0fd927c1
2024-11-03 12:01:43## It arrived! I was feeling impatient, waiting for my snazzy, brand-spanking new mobile phone to arrive, but when it got here, I just stared at the box, in trepidation. Everyone kept walking by, asking how it is, but I just shook my head. After nearly four years, with my (originally Android 10), Moto G8 Power, which I loved to death, I wasn't yet ready to move on. I needed a moment, to grieve. RIP, my trusty fren.  ## Anyways... Around 10 pm, I managed to emotionally recover enough to begin the Big Transition, and I was up until 2 am, and still didn't finish. My **SimpleX** database is sort of large, and slow to migrate. Also, took me a while to figure out how to do it, and the whole thing made me terribly nervous, that I'd accidentally get locked out. But it worked, after eight failed attempts, so yay. **Telegram** was back online, almost immediately, since it's tied to the SIM card. Which was convenient, but sorta creeped me out. Our family-internal favorite, **Threema**, was a snap. Took 5 minutes. I had four failed starts with **Slack**, as it kept sending a login code to my Proton Mail, but I didn't have Proton app installed on my new phone, yet, and I was really sleepy, so I kept confirming on the old phone and then Slack would freeze up, and I had to kill the process and restart. My **key manager** is cloud-based, so that went really fast, and I had the nos2x browser extension going in Firefox within 10 minutes, or so. Logged into Habla.News, Nostr.Build, Zap.Cooking, and Nostrudel.Ninja, immediately, so that I can get my Nostr fix. Then I took a deep breath and mass-installed F-Droid, Minibits, **Amethyst**, Citrine, Orbot, and Amber. And breathed out, again, because MIRACLES NEVER CEASE: it seems to be actually working.  Everyone knows that this is the unbeatable Android Nostr setup, but it's also a resource-gobbling monster, that should only be tried at home, kids. Make sure you don't use Amethyst when out-and-about, unless you have a gigantic battery and an unlimited, high-speed, mobile plan. So, basically, everyone in the First World, who isn't me, can do it. Oh, well. At least, I can now indulge over WiFi. The phone itself is just like the old one, but thinner, faster, and doesn't freeze up or take a long time to start. The Motorola is dead. Long live the Motorola.
@ fd208ee8:0fd927c1
2024-11-03 12:01:43## It arrived! I was feeling impatient, waiting for my snazzy, brand-spanking new mobile phone to arrive, but when it got here, I just stared at the box, in trepidation. Everyone kept walking by, asking how it is, but I just shook my head. After nearly four years, with my (originally Android 10), Moto G8 Power, which I loved to death, I wasn't yet ready to move on. I needed a moment, to grieve. RIP, my trusty fren.  ## Anyways... Around 10 pm, I managed to emotionally recover enough to begin the Big Transition, and I was up until 2 am, and still didn't finish. My **SimpleX** database is sort of large, and slow to migrate. Also, took me a while to figure out how to do it, and the whole thing made me terribly nervous, that I'd accidentally get locked out. But it worked, after eight failed attempts, so yay. **Telegram** was back online, almost immediately, since it's tied to the SIM card. Which was convenient, but sorta creeped me out. Our family-internal favorite, **Threema**, was a snap. Took 5 minutes. I had four failed starts with **Slack**, as it kept sending a login code to my Proton Mail, but I didn't have Proton app installed on my new phone, yet, and I was really sleepy, so I kept confirming on the old phone and then Slack would freeze up, and I had to kill the process and restart. My **key manager** is cloud-based, so that went really fast, and I had the nos2x browser extension going in Firefox within 10 minutes, or so. Logged into Habla.News, Nostr.Build, Zap.Cooking, and Nostrudel.Ninja, immediately, so that I can get my Nostr fix. Then I took a deep breath and mass-installed F-Droid, Minibits, **Amethyst**, Citrine, Orbot, and Amber. And breathed out, again, because MIRACLES NEVER CEASE: it seems to be actually working.  Everyone knows that this is the unbeatable Android Nostr setup, but it's also a resource-gobbling monster, that should only be tried at home, kids. Make sure you don't use Amethyst when out-and-about, unless you have a gigantic battery and an unlimited, high-speed, mobile plan. So, basically, everyone in the First World, who isn't me, can do it. Oh, well. At least, I can now indulge over WiFi. The phone itself is just like the old one, but thinner, faster, and doesn't freeze up or take a long time to start. The Motorola is dead. Long live the Motorola. @ fd208ee8:0fd927c1
2024-11-03 09:20:33# It's that season, again I've been growing my hair out (too lazy to cut it) and it has -- once again -- quickly reached a length at which it draws unnecessary attention and sheds everywhere. I suppose it always sheds everywhere, but shedding short hairs is just generally less-gross than finding a 12-inch strand lying on the toast, you were about to consume. So, I'm back to the _50 Shades of Updo_ stage, where I struggle to figure out how to best wear my head, usually defaulting to the _Messy Bun_ look, because it's still too short to do anything more elaborate and looks silly, as a ponytail.   It's really not that great of a look for me, I know, especially, now that my chin is finally succumbing to gravity, but doing something more-elegant is usually more time-consuming and doesn't have that wonderful "swept up" feeling to it. You know that feeling, when you tie all of that heavy hair to a higher point on your skull and the roots just sigh with relief. Another look, I tend to gravitate toward, at the moment, is head scarves, like this one:  ...or a Bavarian-style bandana, for gardening or hiking (don't have a selfie handy, so here is some random chick, who also suffers from poofy, dark hair).  Hiking bare-headed, with flowing tresses, is not recommended, due to all of the Nature, that you have to comb back out of it. Generally, just bored of my inbetween length and looking forward to braiding it, in a few months. Or giving up, in frustration, and cutting it all off.
@ fd208ee8:0fd927c1
2024-11-03 09:20:33# It's that season, again I've been growing my hair out (too lazy to cut it) and it has -- once again -- quickly reached a length at which it draws unnecessary attention and sheds everywhere. I suppose it always sheds everywhere, but shedding short hairs is just generally less-gross than finding a 12-inch strand lying on the toast, you were about to consume. So, I'm back to the _50 Shades of Updo_ stage, where I struggle to figure out how to best wear my head, usually defaulting to the _Messy Bun_ look, because it's still too short to do anything more elaborate and looks silly, as a ponytail.   It's really not that great of a look for me, I know, especially, now that my chin is finally succumbing to gravity, but doing something more-elegant is usually more time-consuming and doesn't have that wonderful "swept up" feeling to it. You know that feeling, when you tie all of that heavy hair to a higher point on your skull and the roots just sigh with relief. Another look, I tend to gravitate toward, at the moment, is head scarves, like this one:  ...or a Bavarian-style bandana, for gardening or hiking (don't have a selfie handy, so here is some random chick, who also suffers from poofy, dark hair).  Hiking bare-headed, with flowing tresses, is not recommended, due to all of the Nature, that you have to comb back out of it. Generally, just bored of my inbetween length and looking forward to braiding it, in a few months. Or giving up, in frustration, and cutting it all off. @ 09fbf8f3:fa3d60f0
2024-11-02 08:00:29> ### 第三方API合集: --- 免责申明: 在此推荐的 OpenAI API Key 由第三方代理商提供,所以我们不对 API Key 的 有效性 和 安全性 负责,请你自行承担购买和使用 API Key 的风险。 | 服务商 | 特性说明 | Proxy 代理地址 | 链接 | | --- | --- | --- | --- | | AiHubMix | 使用 OpenAI 企业接口,全站模型价格为官方 86 折(含 GPT-4 )| https://aihubmix.com/v1 | [官网](https://aihubmix.com?aff=mPS7) | | OpenAI-HK | OpenAI的API官方计费模式为,按每次API请求内容和返回内容tokens长度来定价。每个模型具有不同的计价方式,以每1,000个tokens消耗为单位定价。其中1,000个tokens约为750个英文单词(约400汉字)| https://api.openai-hk.com/ | [官网](https://openai-hk.com/?i=45878) | | CloseAI | CloseAI是国内规模最大的商用级OpenAI代理平台,也是国内第一家专业OpenAI中转服务,定位于企业级商用需求,面向企业客户的线上服务提供高质量稳定的官方OpenAI API 中转代理,是百余家企业和多家科研机构的专用合作平台。 | https://api.openai-proxy.org | [官网](https://www.closeai-asia.com/) | | OpenAI-SB | 需要配合Telegram 获取api key | https://api.openai-sb.com | [官网](https://www.openai-sb.com/) | ` 持续更新。。。` --- ### 推广: 访问不了openai,去`低调云`购买VPN。 官网:https://didiaocloud.xyz 邀请码:`w9AjVJit` 价格低至1元。
@ 09fbf8f3:fa3d60f0
2024-11-02 08:00:29> ### 第三方API合集: --- 免责申明: 在此推荐的 OpenAI API Key 由第三方代理商提供,所以我们不对 API Key 的 有效性 和 安全性 负责,请你自行承担购买和使用 API Key 的风险。 | 服务商 | 特性说明 | Proxy 代理地址 | 链接 | | --- | --- | --- | --- | | AiHubMix | 使用 OpenAI 企业接口,全站模型价格为官方 86 折(含 GPT-4 )| https://aihubmix.com/v1 | [官网](https://aihubmix.com?aff=mPS7) | | OpenAI-HK | OpenAI的API官方计费模式为,按每次API请求内容和返回内容tokens长度来定价。每个模型具有不同的计价方式,以每1,000个tokens消耗为单位定价。其中1,000个tokens约为750个英文单词(约400汉字)| https://api.openai-hk.com/ | [官网](https://openai-hk.com/?i=45878) | | CloseAI | CloseAI是国内规模最大的商用级OpenAI代理平台,也是国内第一家专业OpenAI中转服务,定位于企业级商用需求,面向企业客户的线上服务提供高质量稳定的官方OpenAI API 中转代理,是百余家企业和多家科研机构的专用合作平台。 | https://api.openai-proxy.org | [官网](https://www.closeai-asia.com/) | | OpenAI-SB | 需要配合Telegram 获取api key | https://api.openai-sb.com | [官网](https://www.openai-sb.com/) | ` 持续更新。。。` --- ### 推广: 访问不了openai,去`低调云`购买VPN。 官网:https://didiaocloud.xyz 邀请码:`w9AjVJit` 价格低至1元。 @ f462d21e:1390b6b1
2024-11-02 05:29:26eyJfaWQiOiIwMjkwMWQ4Yi04YWFhLTRiMTYtYWZhOS0wMTMzMGY4MTI4YzEiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX0JVWSIsImNvdW50cnkiOiJGcmFuY2UiLCJjb3VudHJ5Q29kZSI6IkZSIiwibGF0IjpudWxsLCJsb24iOm51bGwsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiQ1JZUFRPQ1VSUkVOQ1kiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJtYXJrZXRQcmljZSI6bnVsbCwiZml4ZWRQcmljZSI6MTQ5LCJidXllclNldHRsZW1lbnRBZGRyZXNzIjoiODg4dE5rWnJQTjZKc0VnZWtqTW5BQlU0VEJ6YzJEdDI5RVBBdmtSeGJBTnNBbmp5UGJiM2lRMVlCUmsxVVhjZFJzaUtjOWRod01WZ041UzljUVVpeW9vZ0RhdnVwM0giLCJtaW5BbW91bnQiOjIwMCwibWF4QW1vdW50IjoyMDAwLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCBjcnlwdG8gdHJhZGVyIiwibXNnIjoic2NhbW1lcnMgaGF2ZSBubyBjaGFuY2UuIHByb2l2ZGUgYmxvY2tjaGFpbiBsaW5rIGFmdGVyIHBheW1lbnQiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInJlcXVpcmVGZWVkYmFja1Njb3JlIjpudWxsLCJmaXJzdFRpbWVMaW1pdEFzc2V0IjpudWxsLCJwYXltZW50V2luZG93TWludXRlcyI6NjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDJUMDU6Mjk6MjYuNzQ1WiJ9
@ f462d21e:1390b6b1
2024-11-02 05:29:26eyJfaWQiOiIwMjkwMWQ4Yi04YWFhLTRiMTYtYWZhOS0wMTMzMGY4MTI4YzEiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX0JVWSIsImNvdW50cnkiOiJGcmFuY2UiLCJjb3VudHJ5Q29kZSI6IkZSIiwibGF0IjpudWxsLCJsb24iOm51bGwsImN1cnJlbmN5Q29kZSI6IlVTRCIsInBheW1lbnRNZXRob2RDb2RlIjoiQ1JZUFRPQ1VSUkVOQ1kiLCJwcmljZUlucHV0VHlwZSI6IkZJWEVEIiwibWFyZ2luIjowLCJtYXJrZXRQcmljZSI6bnVsbCwiZml4ZWRQcmljZSI6MTQ5LCJidXllclNldHRsZW1lbnRBZGRyZXNzIjoiODg4dE5rWnJQTjZKc0VnZWtqTW5BQlU0VEJ6YzJEdDI5RVBBdmtSeGJBTnNBbmp5UGJiM2lRMVlCUmsxVVhjZFJzaUtjOWRod01WZ041UzljUVVpeW9vZ0RhdnVwM0giLCJtaW5BbW91bnQiOjIwMCwibWF4QW1vdW50IjoyMDAwLCJsaW1pdFRvRmlhdEFtb3VudHMiOiIiLCJwYXltZW50TWV0aG9kRGV0YWlsIjoiYmVzdCBjcnlwdG8gdHJhZGVyIiwibXNnIjoic2NhbW1lcnMgaGF2ZSBubyBjaGFuY2UuIHByb2l2ZGUgYmxvY2tjaGFpbiBsaW5rIGFmdGVyIHBheW1lbnQiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInJlcXVpcmVGZWVkYmFja1Njb3JlIjpudWxsLCJmaXJzdFRpbWVMaW1pdEFzc2V0IjpudWxsLCJwYXltZW50V2luZG93TWludXRlcyI6NjAsImhpZGRlbiI6ZmFsc2UsImJhbm5lZCI6ZmFsc2UsInZlcmlmaWVkIjp0cnVlLCJhZGRlZCI6IjIwMjQtMTEtMDJUMDU6Mjk6MjYuNzQ1WiJ9 @ f462d21e:1390b6b1
2024-11-01 22:45:56deleted
@ f462d21e:1390b6b1
2024-11-01 22:45:56deleted @ a95c6243:d345522c
2024-11-01 18:22:43*Die «moralische Weltordnung» – eine Art Astrologie. Friedrich Nietzsche* **Das Treffen der BRICS-Staaten beim [Gipfel](https://transition-news.org/brics-gipfel-in-kasan-warum-schweigt-die-schweiz) im russischen Kasan** war sicher nicht irgendein politisches Event. Gastgeber Wladimir Putin habe «Hof gehalten», sagen die Einen, China und Russland hätten ihre Vorstellung einer multipolaren Weltordnung zelebriert, schreiben Andere. **In jedem Fall zeigt die Anwesenheit von über 30 Delegationen aus der ganzen Welt,** dass von einer geostrategischen Isolation Russlands wohl keine Rede sein kann. Darüber hinaus haben sowohl die Anreise von UN-Generalsekretär António Guterres als auch die Meldungen und Dementis bezüglich der Beitrittsbemühungen des NATO-Staats [Türkei](https://transition-news.org/turkei-entlarvt-fake-news-von-bild-uber-indiens-angebliches-veto-gegen-den) für etwas Aufsehen gesorgt. **Im Spannungsfeld geopolitischer und wirtschaftlicher Umbrüche** zeigt die neue Allianz zunehmendes Selbstbewusstsein. In Sachen gemeinsamer Finanzpolitik schmiedet man interessante Pläne. Größere Unabhängigkeit von der US-dominierten Finanzordnung ist dabei ein wichtiges Ziel. **Beim BRICS-Wirtschaftsforum in Moskau, wenige Tage vor dem Gipfel,** zählte ein nachhaltiges System für Finanzabrechnungen und Zahlungsdienste zu den vorrangigen Themen. Während dieses Treffens ging der russische Staatsfonds eine Partnerschaft mit dem Rechenzentrumsbetreiber BitRiver ein, um [Bitcoin](https://www.forbes.com/sites/digital-assets/2024/10/23/russia-launches-brics-mining-infrastructure-project/)-Mining-Anlagen für die BRICS-Länder zu errichten. **Die Initiative könnte ein Schritt sein, Bitcoin und andere Kryptowährungen** als Alternativen zu traditionellen Finanzsystemen zu etablieren. Das Projekt könnte dazu führen, dass die BRICS-Staaten den globalen Handel in Bitcoin abwickeln. Vor dem Hintergrund der Diskussionen über eine «BRICS-Währung» wäre dies eine Alternative zu dem ursprünglich angedachten Korb lokaler Währungen und zu goldgedeckten Währungen sowie eine mögliche Ergänzung zum Zahlungssystem [BRICS Pay](https://en.wikipedia.org/wiki/BRICS_PAY). **Dient der Bitcoin also der Entdollarisierung?** Oder droht er inzwischen, zum Gegenstand geopolitischer [Machtspielchen](https://legitim.ch/es-ist-ein-sieg-fuer-bitcoin-waehrend-russland-und-die-usa-um-die-krypto-vorherrschaft-kaempfen/) zu werden? Angesichts der globalen Vernetzungen ist es oft schwer zu durchschauen, «was eine Show ist und was im Hintergrund von anderen Strippenziehern insgeheim gesteuert wird». Sicher können Strukturen wie Bitcoin auch so genutzt werden, dass sie den Herrschenden dienlich sind. Aber die Grundeigenschaft des dezentralisierten, unzensierbaren Peer-to-Peer Zahlungsnetzwerks ist ihm schließlich nicht zu nehmen. **Wenn es nach der EZB oder dem IWF geht, dann scheint statt Instrumentalisierung** momentan eher der Kampf gegen Kryptowährungen angesagt. Jürgen Schaaf, Senior Manager bei der Europäischen Zentralbank, hat jedenfalls dazu aufgerufen, [Bitcoin «zu eliminieren»](https://www.btc-echo.de/schlagzeilen/ezb-banker-es-gibt-gute-gruende-bitcoin-zu-eliminieren-194015/). Der Internationale Währungsfonds forderte El Salvador, das Bitcoin 2021 als gesetzliches Zahlungsmittel eingeführt hat, kürzlich zu [begrenzenden Maßnahmen](https://legitim.ch/el-salvador-iwf-fordert-trotz-nicht-eingetretener-risiken-neue-massnahmen-gegen-bitcoin/) gegen das Kryptogeld auf. **Dass die BRICS-Staaten ein freiheitliches Ansinnen im Kopf haben,** wenn sie Kryptowährungen ins Spiel bringen, darf indes auch bezweifelt werden. Im [Abschlussdokument](http://static.kremlin.ru/media/events/files/en/RosOySvLzGaJtmx2wYFv0lN4NSPZploG.pdf) bekennen sich die Gipfel-Teilnehmer ausdrücklich zur UN, ihren Programmen und ihrer «Agenda 2030». Ernst Wolff nennt das «eine [Bankrotterklärung](https://x.com/wolff_ernst/status/1849781982961557771) korrupter Politiker, die sich dem digital-finanziellen Komplex zu 100 Prozent unterwerfen». --- Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/aufstand-gegen-die-dollar-hegemonie)* erschienen.
@ a95c6243:d345522c
2024-11-01 18:22:43*Die «moralische Weltordnung» – eine Art Astrologie. Friedrich Nietzsche* **Das Treffen der BRICS-Staaten beim [Gipfel](https://transition-news.org/brics-gipfel-in-kasan-warum-schweigt-die-schweiz) im russischen Kasan** war sicher nicht irgendein politisches Event. Gastgeber Wladimir Putin habe «Hof gehalten», sagen die Einen, China und Russland hätten ihre Vorstellung einer multipolaren Weltordnung zelebriert, schreiben Andere. **In jedem Fall zeigt die Anwesenheit von über 30 Delegationen aus der ganzen Welt,** dass von einer geostrategischen Isolation Russlands wohl keine Rede sein kann. Darüber hinaus haben sowohl die Anreise von UN-Generalsekretär António Guterres als auch die Meldungen und Dementis bezüglich der Beitrittsbemühungen des NATO-Staats [Türkei](https://transition-news.org/turkei-entlarvt-fake-news-von-bild-uber-indiens-angebliches-veto-gegen-den) für etwas Aufsehen gesorgt. **Im Spannungsfeld geopolitischer und wirtschaftlicher Umbrüche** zeigt die neue Allianz zunehmendes Selbstbewusstsein. In Sachen gemeinsamer Finanzpolitik schmiedet man interessante Pläne. Größere Unabhängigkeit von der US-dominierten Finanzordnung ist dabei ein wichtiges Ziel. **Beim BRICS-Wirtschaftsforum in Moskau, wenige Tage vor dem Gipfel,** zählte ein nachhaltiges System für Finanzabrechnungen und Zahlungsdienste zu den vorrangigen Themen. Während dieses Treffens ging der russische Staatsfonds eine Partnerschaft mit dem Rechenzentrumsbetreiber BitRiver ein, um [Bitcoin](https://www.forbes.com/sites/digital-assets/2024/10/23/russia-launches-brics-mining-infrastructure-project/)-Mining-Anlagen für die BRICS-Länder zu errichten. **Die Initiative könnte ein Schritt sein, Bitcoin und andere Kryptowährungen** als Alternativen zu traditionellen Finanzsystemen zu etablieren. Das Projekt könnte dazu führen, dass die BRICS-Staaten den globalen Handel in Bitcoin abwickeln. Vor dem Hintergrund der Diskussionen über eine «BRICS-Währung» wäre dies eine Alternative zu dem ursprünglich angedachten Korb lokaler Währungen und zu goldgedeckten Währungen sowie eine mögliche Ergänzung zum Zahlungssystem [BRICS Pay](https://en.wikipedia.org/wiki/BRICS_PAY). **Dient der Bitcoin also der Entdollarisierung?** Oder droht er inzwischen, zum Gegenstand geopolitischer [Machtspielchen](https://legitim.ch/es-ist-ein-sieg-fuer-bitcoin-waehrend-russland-und-die-usa-um-die-krypto-vorherrschaft-kaempfen/) zu werden? Angesichts der globalen Vernetzungen ist es oft schwer zu durchschauen, «was eine Show ist und was im Hintergrund von anderen Strippenziehern insgeheim gesteuert wird». Sicher können Strukturen wie Bitcoin auch so genutzt werden, dass sie den Herrschenden dienlich sind. Aber die Grundeigenschaft des dezentralisierten, unzensierbaren Peer-to-Peer Zahlungsnetzwerks ist ihm schließlich nicht zu nehmen. **Wenn es nach der EZB oder dem IWF geht, dann scheint statt Instrumentalisierung** momentan eher der Kampf gegen Kryptowährungen angesagt. Jürgen Schaaf, Senior Manager bei der Europäischen Zentralbank, hat jedenfalls dazu aufgerufen, [Bitcoin «zu eliminieren»](https://www.btc-echo.de/schlagzeilen/ezb-banker-es-gibt-gute-gruende-bitcoin-zu-eliminieren-194015/). Der Internationale Währungsfonds forderte El Salvador, das Bitcoin 2021 als gesetzliches Zahlungsmittel eingeführt hat, kürzlich zu [begrenzenden Maßnahmen](https://legitim.ch/el-salvador-iwf-fordert-trotz-nicht-eingetretener-risiken-neue-massnahmen-gegen-bitcoin/) gegen das Kryptogeld auf. **Dass die BRICS-Staaten ein freiheitliches Ansinnen im Kopf haben,** wenn sie Kryptowährungen ins Spiel bringen, darf indes auch bezweifelt werden. Im [Abschlussdokument](http://static.kremlin.ru/media/events/files/en/RosOySvLzGaJtmx2wYFv0lN4NSPZploG.pdf) bekennen sich die Gipfel-Teilnehmer ausdrücklich zur UN, ihren Programmen und ihrer «Agenda 2030». Ernst Wolff nennt das «eine [Bankrotterklärung](https://x.com/wolff_ernst/status/1849781982961557771) korrupter Politiker, die sich dem digital-finanziellen Komplex zu 100 Prozent unterwerfen». --- Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/aufstand-gegen-die-dollar-hegemonie)* erschienen. @ c69b71dc:426ba763
2024-10-31 16:02:10# Risks and Regulations ### Food contact materials (FCMs) Materials that come into contact with food during processing, packaging, or transport – play a critical role in food safety. However, chemicals can migrate from these materials into food, introducing potential health risks. For instance, chemicals can leach into food from packaging materials, especially during microwaving, pasteurization, or other high-temperature exposures. Even printing inks on the outer packaging, if not well-contained, can migrate into the food or drink. Factors like high temperatures, small package-to-food ratios, fatty foods, and long storage times all increase this risk. More than 12,200 chemicals have been identified in FCMs, but only about 100 substances are regulated by the European Union, focusing mainly on plastics. The actual composition of many materials is often undisclosed due to proprietary protection, making it challenging to assess risks fully. Even less is known about secondary substances, which may arise from additives breaking down during manufacturing.  > In 2016, EU regulation defined publicly that *current regulations do not sufficiently protect public health from the harmful impacts of chemicals migrating from food packaging.* The current paradigm for evaluating the safety of FCMs is insufficient, as there is a general underestimation of the role of FCMs in food contamination and a lack of information on human exposure. FCMs are a significant source of human exposure to chemicals of concern, including perfluorinated compounds (PFCs) and endocrine-disrupting chemicals (EDCs), as well as those linked to neurodevelopmental issues. Moreover, the legal framework doesn’t account for the cumulative "cocktail effect" of multiple low-level chemical exposures, which can collectively exceed safe limits. Research shows that FCMs can contribute to serious health issues like cardiovascular disease, diabetes, obesity, neurological disorders, and cancer. Although packaging is designed to preserve food, maintain quality, and extend shelf life, its chemical impacts remain insufficiently regulated, posing risks that demand greater transparency and robust oversight. ### So what can we do? Be mindful and use less packaged food. Plastic is sometimes even less harmful than paper, as many chemicals and synthetic materials are used in paper production to improve texture and prevent humidity from transferring through the paper packaging. Additionally, the barrier between ink and food in paper packaging is often not very effective. Chemicals are mostly invisible...! 
@ c69b71dc:426ba763
2024-10-31 16:02:10# Risks and Regulations ### Food contact materials (FCMs) Materials that come into contact with food during processing, packaging, or transport – play a critical role in food safety. However, chemicals can migrate from these materials into food, introducing potential health risks. For instance, chemicals can leach into food from packaging materials, especially during microwaving, pasteurization, or other high-temperature exposures. Even printing inks on the outer packaging, if not well-contained, can migrate into the food or drink. Factors like high temperatures, small package-to-food ratios, fatty foods, and long storage times all increase this risk. More than 12,200 chemicals have been identified in FCMs, but only about 100 substances are regulated by the European Union, focusing mainly on plastics. The actual composition of many materials is often undisclosed due to proprietary protection, making it challenging to assess risks fully. Even less is known about secondary substances, which may arise from additives breaking down during manufacturing.  > In 2016, EU regulation defined publicly that *current regulations do not sufficiently protect public health from the harmful impacts of chemicals migrating from food packaging.* The current paradigm for evaluating the safety of FCMs is insufficient, as there is a general underestimation of the role of FCMs in food contamination and a lack of information on human exposure. FCMs are a significant source of human exposure to chemicals of concern, including perfluorinated compounds (PFCs) and endocrine-disrupting chemicals (EDCs), as well as those linked to neurodevelopmental issues. Moreover, the legal framework doesn’t account for the cumulative "cocktail effect" of multiple low-level chemical exposures, which can collectively exceed safe limits. Research shows that FCMs can contribute to serious health issues like cardiovascular disease, diabetes, obesity, neurological disorders, and cancer. Although packaging is designed to preserve food, maintain quality, and extend shelf life, its chemical impacts remain insufficiently regulated, posing risks that demand greater transparency and robust oversight. ### So what can we do? Be mindful and use less packaged food. Plastic is sometimes even less harmful than paper, as many chemicals and synthetic materials are used in paper production to improve texture and prevent humidity from transferring through the paper packaging. Additionally, the barrier between ink and food in paper packaging is often not very effective. Chemicals are mostly invisible...!  @ cf5b8c65:494a0912
2024-10-31 11:55:39Estoy probando un plugin para Obisidian que permite publicar directamente en NOSTR los artículos que has creado en Obsidian.
@ cf5b8c65:494a0912
2024-10-31 11:55:39Estoy probando un plugin para Obisidian que permite publicar directamente en NOSTR los artículos que has creado en Obsidian. @ fd208ee8:0fd927c1
2024-10-31 11:03:08## Chef's notes I got the recipe from the [byanjushka website](https://byanjushka.com/erdnussbutter-kekse-rezept-8177/). She includes a lot more information on there, and lots of pictures and instructions. But it's all in German, so here's my quickie, English version. I've doubled the amounts, as I first baked this for the #PurpleKonnektiv meetup, and I knew I'd have some hungry guests. The cookies are vegan, but they're mostly just peanut, so it's sort of irrelevant. Just make sure you get the really high-quality peanut butter that is 100% peanut. You can usually identify it by the fact that the oil separates from the base, a bit. Everything else is probably with hardened palm oil, or something. ## Details - ⏲️ Prep time: 15 min - 🍳 Cook time: 10 min - 🍽️ Servings: 30 cookies ## Ingredients - 500 g peanut butter, normal or crunchy - 300 g brown (or raw) sugar - 160 ml plant-based milk (or cows' milk, if you don't care about vegan) - 1 pkg vanilla sugar (bourbon is nice) or 1 tsp vanilla - 250 g flour - 2 tsp baking powder - 2/3 tsp salt ## Directions 1. Preheat oven to 180 °C (350 °F). 2. Beat together the peanut butter and the sugars, with an electric mixer. 3. Mix in milk and vanilla. 4. In a separate bowl, stir together flour, salt, and baking powder. 5. Stir the dry ingredients into the wet ingredients, and then knead the dough a bit. 6. (At this point, I put the dough in the fridge overnight, and baked it the next day.) 7. Line your baking sheet with baking paper. 8. Form tbsp-spoon-sized balls of dough. 9. Press each one flat, with a fork, dipping the fork in water, before each press (to keep the dough from sticking to the fork).
@ fd208ee8:0fd927c1
2024-10-31 11:03:08## Chef's notes I got the recipe from the [byanjushka website](https://byanjushka.com/erdnussbutter-kekse-rezept-8177/). She includes a lot more information on there, and lots of pictures and instructions. But it's all in German, so here's my quickie, English version. I've doubled the amounts, as I first baked this for the #PurpleKonnektiv meetup, and I knew I'd have some hungry guests. The cookies are vegan, but they're mostly just peanut, so it's sort of irrelevant. Just make sure you get the really high-quality peanut butter that is 100% peanut. You can usually identify it by the fact that the oil separates from the base, a bit. Everything else is probably with hardened palm oil, or something. ## Details - ⏲️ Prep time: 15 min - 🍳 Cook time: 10 min - 🍽️ Servings: 30 cookies ## Ingredients - 500 g peanut butter, normal or crunchy - 300 g brown (or raw) sugar - 160 ml plant-based milk (or cows' milk, if you don't care about vegan) - 1 pkg vanilla sugar (bourbon is nice) or 1 tsp vanilla - 250 g flour - 2 tsp baking powder - 2/3 tsp salt ## Directions 1. Preheat oven to 180 °C (350 °F). 2. Beat together the peanut butter and the sugars, with an electric mixer. 3. Mix in milk and vanilla. 4. In a separate bowl, stir together flour, salt, and baking powder. 5. Stir the dry ingredients into the wet ingredients, and then knead the dough a bit. 6. (At this point, I put the dough in the fridge overnight, and baked it the next day.) 7. Line your baking sheet with baking paper. 8. Form tbsp-spoon-sized balls of dough. 9. Press each one flat, with a fork, dipping the fork in water, before each press (to keep the dough from sticking to the fork). @ eac63075:b4988b48
2024-10-30 20:58:01Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions. https://www.fountain.fm/episode/hVVS7hrsX8VQ9SPoUYbg ## What Are Cryptocurrencies? Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably. ## The Origin of the Myth: Cryptocurrencies and Illicit Activities The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use. ## Current Data: Cryptocurrencies and Illicit Activities [According to the **2024 Cryptocurrency Crime Report** from **Chainalysis**](https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/?ref=eddieoz.com), only **0.34%** of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities. ## Comparison with Traditional Money When we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. [According to a report by **Verafin**](https://verafin.com/2024/02/a-3-1-trillion-financial-crime-epidemic/?ref=eddieoz.com), about **3.1 trillion dollars** are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately **3.87%** of all money in circulation. In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies. ## The Transparency of Blockchain One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record. Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace. ## How Much Money Is There in the World? To understand the scale, it’s interesting to know that, according to the **World Population Review**, [about **80 trillion dollars** are in circulation globally](https://worldpopulationreview.com/metrics/how-much-money-is-in-the-world?ref=eddieoz.com), including physical and digital money. Out of this total, only **5 trillion dollars** is in physical cash. This shows that most transactions are already digital, even in the traditional financial system. 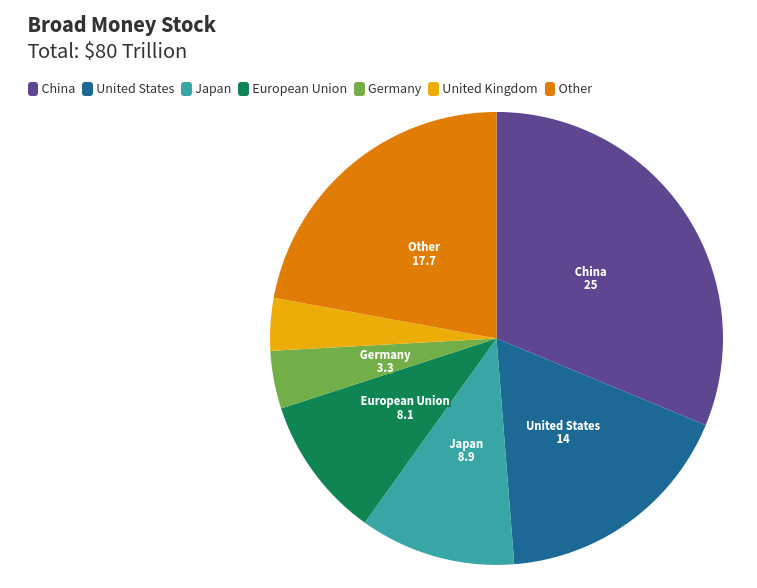## Cryptocurrencies Promote Economic Freedom Cryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services. This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them. ## Myths and Realities It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation. ## Conclusion: Are Cryptocurrencies Really the Villains? The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception. If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause. ## And You, What Do You Think? Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion!Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions. What Are Cryptocurrencies? Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably. The Origin of the Myth: Cryptocurrencies and Illicit Activities The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use. Current Data: Cryptocurrencies and Illicit Activities According to the 2024 Cryptocurrency Crime Report from Chainalysis, only 0.34% of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities. Comparison with Traditional Money When we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. According to a report by Verafin, about 3.1 trillion dollars are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately 3.87% of all money in circulation. In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies. The Transparency of Blockchain One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record. Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace. How Much Money Is There in the World? To understand the scale, it’s interesting to know that, according to the World Population Review, about 80 trillion dollars are in circulation globally, including physical and digital money. Out of this total, only 5 trillion dollars is in physical cash. This shows that most transactions are already digital, even in the traditional financial system. Cryptocurrencies Promote Economic Freedom Cryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services. This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them. Myths and Realities It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation. Conclusion: Are Cryptocurrencies Really the Villains? The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception. If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause. And You, What Do You Think? Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion!
@ eac63075:b4988b48
2024-10-30 20:58:01Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions. https://www.fountain.fm/episode/hVVS7hrsX8VQ9SPoUYbg ## What Are Cryptocurrencies? Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably. ## The Origin of the Myth: Cryptocurrencies and Illicit Activities The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use. ## Current Data: Cryptocurrencies and Illicit Activities [According to the **2024 Cryptocurrency Crime Report** from **Chainalysis**](https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/?ref=eddieoz.com), only **0.34%** of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities. ## Comparison with Traditional Money When we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. [According to a report by **Verafin**](https://verafin.com/2024/02/a-3-1-trillion-financial-crime-epidemic/?ref=eddieoz.com), about **3.1 trillion dollars** are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately **3.87%** of all money in circulation. In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies. ## The Transparency of Blockchain One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record. Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace. ## How Much Money Is There in the World? To understand the scale, it’s interesting to know that, according to the **World Population Review**, [about **80 trillion dollars** are in circulation globally](https://worldpopulationreview.com/metrics/how-much-money-is-in-the-world?ref=eddieoz.com), including physical and digital money. Out of this total, only **5 trillion dollars** is in physical cash. This shows that most transactions are already digital, even in the traditional financial system. 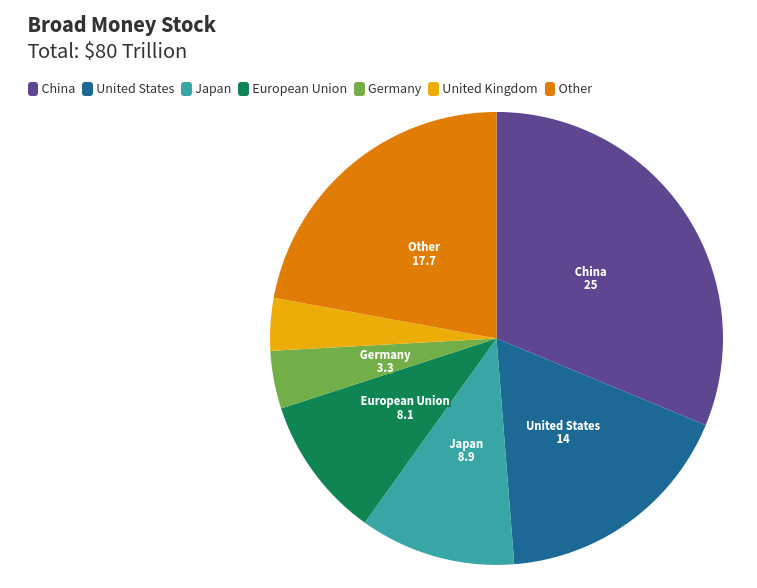## Cryptocurrencies Promote Economic Freedom Cryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services. This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them. ## Myths and Realities It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation. ## Conclusion: Are Cryptocurrencies Really the Villains? The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception. If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause. ## And You, What Do You Think? Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion!Have you ever heard that cryptocurrencies are primarily used by criminals? This is a common idea, but it doesn’t reflect reality. In this article, we will explore what cryptocurrencies are, how they work, and why the notion that they’re only for illegal activities is a myth. We will also compare the use of cryptocurrencies with traditional money and understand how blockchain technology brings transparency and security to transactions. What Are Cryptocurrencies? Cryptocurrencies are digital currencies that use cryptography to secure transactions. The most well-known is Bitcoin, but there are many others, like Ethereum, Litecoin, and Ripple. Unlike traditional money, cryptocurrencies are not controlled by governments or central banks. They operate on a decentralized network called blockchain, which records all transactions publicly and immutably. The Origin of the Myth: Cryptocurrencies and Illicit Activities The myth that cryptocurrencies are mainly used for crime began with cases like Silk Road, an illegal online marketplace where Bitcoin was used to buy and sell illicit products. This type of news captured attention and created a negative image of cryptocurrencies. However, it’s essential to understand that these cases are exceptions and don’t represent the majority of cryptocurrency use. Current Data: Cryptocurrencies and Illicit Activities According to the 2024 Cryptocurrency Crime Report from Chainalysis, only 0.34% of cryptocurrency transactions in 2023 were linked to illegal activities. This means that the vast majority of people use cryptocurrencies legitimately, for investments, shopping, sending money to family in other countries, and other legal activities. Comparison with Traditional Money When we look at traditional money, like the dollar or the euro, we see that it is much more used in criminal activities. According to a report by Verafin, about 3.1 trillion dollars are used annually in financial crimes such as drug trafficking, terrorism, fraud, and money laundering. This represents approximately 3.87% of all money in circulation. In comparison, the illicit use of cryptocurrencies is a much smaller fraction. This shows that traditional money remains the main tool for financial crimes, not cryptocurrencies. The Transparency of Blockchain One of the great advantages of cryptocurrencies is blockchain technology. Since all transactions are recorded in a public ledger, it’s possible to trace the path of money. This makes it harder for criminals to hide their activities. Unlike cash, which can change hands without leaving any trace, cryptocurrency transactions leave a permanent record. Companies and law enforcement agencies use this transparency to identify and combat illegal activities. This makes cryptocurrencies less appealing to criminals who prefer methods that leave no trace. How Much Money Is There in the World? To understand the scale, it’s interesting to know that, according to the World Population Review, about 80 trillion dollars are in circulation globally, including physical and digital money. Out of this total, only 5 trillion dollars is in physical cash. This shows that most transactions are already digital, even in the traditional financial system. Cryptocurrencies Promote Economic Freedom Cryptocurrencies offer people more control over their own money. Without the need for intermediaries like banks or governments, transactions can be made directly between individuals. This is especially useful in countries with unstable financial systems or where the population lacks easy access to banking services. This financial autonomy can bother traditional institutions that are used to controlling the flow of money. Therefore, we sometimes see criticism of cryptocurrencies from these institutions, which may try to link them to criminal activities to discredit them. Myths and Realities It’s a myth to say that cryptocurrencies are mainly used for crimes. The reality is that they are primarily used for legal and legitimate purposes. People around the world invest in cryptocurrencies, use them for online shopping, send money to family in other countries, and even protect their savings from inflation. Conclusion: Are Cryptocurrencies Really the Villains? The evidence shows that cryptocurrencies are not the villains some believe them to be. On the contrary, they offer a safe, transparent, and efficient way to conduct financial transactions. While traditional money continues to be the main means used in criminal activities, the illicit use of cryptocurrencies remains a small exception. If you have doubts about the reliability of cryptocurrencies, remember that the technology behind them is designed to be safe and transparent. With current data and information, it’s clear that cryptocurrencies are closer to being a solution for financial problems than a cause. And You, What Do You Think? Are cryptocurrencies being unfairly accused? Share your opinion and join the discussion! @ 8f69ac99:4f92f5fd
2024-10-30 14:54:26Nos últimos anos, a narrativa dominante retrata a mineração de Bitcoin como um consumidor voraz de energia, com impactos ambientais desproporcionais. Embora a mineração de Bitcoin exija uma quantidade significativa de energia, esta visão ignora um ponto crucial: o seu potencial para promover a sustentabilidade ambiental e remodelar a integração de energias renováveis. Este artigo vai além dos debates convencionais sobre a pegada de carbono, explorando como a mineração de Bitcoin pode mitigar os impactos ambientais e catalisar uma transição energética sustentável, transformando o que alguns consideram uma inutilidade num aliado contra a dependência dos combustíveis fósseis e a adversidade climática. --- ### **Desafios da Energia Renovável** Alcançar um futuro sustentável depende da adopção de fontes de energia renovável, mas estas enfrentam desafios únicos. Gerir o excesso de energia produzido durante períodos de baixa procura e lidar com as limitações da actual tecnologia de baterias são obstáculos significativos. Além disso, a transmissão de energia a longas distâncias permanece ineficiente, o que impede que recursos renováveis remotos alcancem mercados mais amplos. Por exemplo, as linhas de corrente contínua de alta tensão (HVDC) perdem aproximadamente 3% de potência por cada 1.000 km, enquanto as linhas de corrente alternada de alta tensão (HVAC) perdem cerca de 7% por cada 1.000 km. Isto significa que, por cada quilómetro, as linhas HVDC perdem cerca de 0,003%, e as linhas HVAC perdem cerca de 0,007% (as linhas de alta tensão são projectadas para diminuir perdas, as perdas são ainda maiores na media tensão). Estas perdas, aliadas à dificuldade de transportar energia de parques renováveis remotos, sublinham a necessidade de soluções localizadas. Por exemplo, em 2018, cerca de 6,5 milhões de MWh de produção de energia solar fotovoltaica foram descartados, ou "mandados fora", no Chile, na China, na Alemanha e nos Estados Unidos conjuntamente. É importante notar que, à medida que a capacidade de energia renovável continua a crescer rapidamente (com o aumento das adições de capacidade renovável global anual em quase 50%, para quase 510 gigawatts em 2023), a quantidade absoluta de energia desperdiçada é susceptível de aumentar, a menos que se façam melhorias significativas na infraestrutura da rede, no armazenamento de energia e na gestão da procura. ### **Monetizar o Excesso de Energia através da Mineração de Bitcoin** Fontes de energia renovável, como a solar e a eólica, muitas vezes geram mais electricidade do que a rede necessita em determinados momentos, criando um excedente de energia que normalmente é desperdiçado. Este excesso permanece subutilizado porque: - As soluções de armazenamento em grande escala são limitadas e dispendiosas ou mesmo inexistentes; - A capacidade de transmissão muitas vezes não é suficiente para distribuir energia a longas distâncias; - E a procura nem sempre coincide com os períodos de produção máxima de energia renovável. A mineração de Bitcoin apresenta uma solução apelativa, ao actuar como um consumidor de energia flexível, capaz de ajustar rapidamente o seu consumo para se alinhar com a oferta. Operações de mineração localizadas perto de instalações de energia renovável — como centrais hidroeléctricas ou parques solares — podem absorver o excesso de energia que, de outra forma, seria desperdiçado, monetizando-o. Esta configuração não só reduz o desperdício de energia renovável, como também proporciona fontes de rendimento fiáveis para projectos renováveis, incentivando o investimento em infraestruturas verdes. #### **Mineração de Bitcoin como Consumidor Flexível** As operações de mineração de Bitcoin podem ajustar dinamicamente o seu consumo de energia, actuando como uma "carga flexível" na rede. As principais vantagens incluem: - **Escalabilidade Rápida**: Os equipamentos de mineração podem aumentar ou diminuir o seu consumo de energia quase instantaneamente, respondendo às flutuações na disponibilidade de energia. - **Independência Geográfica**: A mineração de Bitcoin pode ser realizada em qualquer local com ligação à internet, permitindo que os mineradores se situem perto das fontes renováveis, independentemente da infraestrutura da rede. - **Capacidade Modular**: O equipamento de mineração é altamente escalável, permitindo que os produtores de energia desenhem sistemas modulares que se adaptem à capacidade energética disponível. #### **Incentivos Económicos e Benefícios** A utilização do excedente de energia para a mineração de Bitcoin permite que os produtores de energia renovável gerem receitas a partir de energia que, de outra forma, seria desperdiçada. Este impulso económico aumenta a rentabilidade dos projectos de energia renovável, tornando-os mais atractivos para os investidores. Os benefícios adicionais incluem: - **Estabilização da Rede**: As operações de mineração ajudam a equilibrar a oferta e a procura na rede, contribuindo para a resiliência e estabilidade da mesma. - **Redução do Desperdício**: Ao consumir electricidade excedente, a mineração de Bitcoin reduz significativamente a quantidade de energia renovável desperdiçada. - **Aumento do Financiamento para Renováveis**: Os lucros provenientes da mineração de Bitcoin podem ser reinvestidos em novos projectos de energia renovável, soluções de armazenamento e infraestrutura de rede, criando um ciclo positivo de reforço para a energia verde. #### **Aplicações no Mundo Real** Vários exemplos ilustram como a mineração de Bitcoin monetiza eficazmente o excedente de energia: - No Texas, os mineradores de Bitcoin aproveitam o excesso de energia eólica, apoiando a rede através de programas de resposta à procura que aumentam a fiabilidade da rede durante períodos de alta e baixa procura. - No [Quebec](https://d-central.tech/the-untapped-potential-advocating-for-bitcoin-mining-as-a-key-to-quebecs-energy-future/), o excesso de energia hidroeléctrica é canalizado para operações de mineração de Bitcoin, o que ajuda a estabilizar a rede e a reduzir o desperdício de energia renovável. - Um [estudo](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development) da Universidade de Cornell descobriu que projectos de energia renovável nos EUA poderiam gerar milhões de dólares ao minerar Bitcoin durante estágios pré-comerciais, demonstrando a viabilidade económica desta abordagem. #### **Potencial Impacto na Transição para Energias Renováveis** Ao monetizar o excedente de energia através da mineração de Bitcoin, esta abordagem acelera a transição para energias renováveis. Os benefícios incluem: - **Viabilidade Económica para Renováveis**: A monetização da energia desperdiçada torna os projectos renováveis mais rentáveis e, portanto, mais atractivos para investidores. - **Flexibilidade da Rede**: A mineração de Bitcoin fornece uma fonte de procura escalável e adaptável, ajudando os operadores de rede a gerir as flutuações de oferta. - **Pegada de Carbono Reduzida**: Ao utilizar fontes renováveis, o impacto ambiental da mineração de Bitcoin diminui, alinhando-se com os objectivos de sustentabilidade. - **Adopção Acelerada de Energias Renováveis**: A maior rentabilidade e a redução do desperdício incentivam um maior investimento, impulsionando a adopção de tecnologias de energia renovável. Essencialmente, a mineração de Bitcoin oferece uma solução única para os desafios da produção intermitente de energia renovável, criando uma procura flexível e independente da localização para a electricidade excedente que, de outra forma, seria desperdiçada. À medida que mais projectos renováveis adoptam este modelo, a mineração de Bitcoin pode desempenhar um papel crucial na promoção de um panorama energético sustentável e descentralizado. ### **Fornecimento de Energia a Regiões Isoladas e Subdesenvolvidas** Um dos impactos mais promissores da mineração de Bitcoin é a capacidade de levar electricidade a regiões remotas e subdesenvolvidas. Pequenas centrais hidroeléctricas e instalações solares são opções cada vez mais viáveis para comunidades isoladas que não têm acesso a redes tradicionais. Mineradores de Bitcoin, em busca de energia barata e excedente, podem apoiar e financiar estas instalações, reduzindo a lacuna energética e permitindo o acesso a energia limpa para estas comunidades. Por exemplo, [aldeias](https://hackernoon.com/no-power-grid-this-african-village-mines-bitcoin-for-electricity) em África que anteriormente não tinham electricidade podem agora operar escolas, clínicas e empresas, graças a pequenos projectos de energia renovável apoiados pela mineração de Bitcoin. Este acesso catalisa o crescimento económico, criando um ciclo virtuoso onde a energia leva a investimentos, educação e melhor saúde — elevando comunidades inteiras para fora da pobreza. ### **Redução de Emissões através da Mitigação de Metano** A mineração de Bitcoin também contribui para a redução das emissões de metano — um gás de efeito estufa com um potencial de aquecimento global 28 a 34 vezes superior ao do CO₂ num período de 100 anos. As emissões de aterros sanitários, resíduos agrícolas e poços de petróleo abandonados representam uma ameaça climática significativa, mas a mineração de Bitcoin oferece uma solução única ao converter este poluente em energia. Quando o metano é queimado para gerar electricidade, é convertido em CO₂ e vapor de água, que, embora também sejam gases de efeito estufa, são muito menos potentes do que o metano. Na verdade, o metano é responsável por cerca de 25% do aquecimento global que experimentamos actualmente, apesar da sua concentração relativamente baixa na atmosfera. Ao capturar e utilizar o metano, as operações de mineração de Bitcoin transformam um dano ambiental numa fonte de energia produtiva, reduzindo as emissões globais de gases de efeito estufa e criando novas fontes de rendimento. Por exemplo, nos EUA, o metano de poços de petróleo abandonados está a ser capturado para alimentar a mineração de Bitcoin, criando um sistema fechado que evita que o metano seja queimado ou liberado directamente na atmosfera. Esta abordagem não só mitiga as emissões, como também apoia o crescimento económico em regiões com recursos de metano não aproveitados. ### **Resiliência e Flexibilidade da Rede** A integração de fontes renováveis, como a eólica e a solar, introduziu desafios para a estabilidade das redes eléctricas. Com as renováveis, os operadores de rede enfrentam flutuações de frequência mais frequentes e uma resposta inercial reduzida — as renováveis não fornecem a mesma resposta inercial que as centrais térmicas tradicionais, tornando a rede mais susceptível a mudanças rápidas. A flexibilidade da mineração de Bitcoin pode desempenhar um papel fundamental na estabilização das redes eléctricas. Durante a tempestade de inverno Uri, no Texas, os mineradores de Bitcoin reduziram o seu consumo de energia para libertar capacidade para serviços essenciais, mostrando o papel da mineração de Bitcoin como uma carga flexível e reactiva de energia. Ao ajustar o consumo de energia com base na disponibilidade de oferta, os mineradores de Bitcoin podem ajudar a equilibrar as redes com elevada penetração de renováveis. Esta sinergia com energias renováveis e nucleares fornece uma solução robusta para a gestão da procura energética, especialmente à medida que a rede transita para fontes de baixo carbono. ### **Impacto Ambiental de Longo Prazo** A mineração de Bitcoin tem o potencial de revolucionar a produção e o consumo de energia. Ao integrar energias renováveis, aproveitar o metano e oferecer gestão flexível da carga, o Bitcoin pode desempenhar um papel fundamental num futuro energético sustentável e descentralizado. Inovação política, responsabilidade industrial e colaboração intersectorial são essenciais para concretizar o potencial do Bitcoin na transição verde. Diante dos desafios ambientais actuais, a mineração de Bitcoin oferece mais do que inovação financeira. Representa um poderoso aliado na construção de um futuro sustentável e equitativo — onde os objectivos digitais e ambientais alinham-se para criar uma economia global mais limpa e resiliente. #Bitcoin #mining #greenEnergy #renewables --- _Photo by [Anders J]("https://unsplash.com/@aj5photos?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash") on [Unsplash]("https://unsplash.com/photos/white-and-blue-solar-panels-hxUcl0nUsIY?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_
@ 8f69ac99:4f92f5fd
2024-10-30 14:54:26Nos últimos anos, a narrativa dominante retrata a mineração de Bitcoin como um consumidor voraz de energia, com impactos ambientais desproporcionais. Embora a mineração de Bitcoin exija uma quantidade significativa de energia, esta visão ignora um ponto crucial: o seu potencial para promover a sustentabilidade ambiental e remodelar a integração de energias renováveis. Este artigo vai além dos debates convencionais sobre a pegada de carbono, explorando como a mineração de Bitcoin pode mitigar os impactos ambientais e catalisar uma transição energética sustentável, transformando o que alguns consideram uma inutilidade num aliado contra a dependência dos combustíveis fósseis e a adversidade climática. --- ### **Desafios da Energia Renovável** Alcançar um futuro sustentável depende da adopção de fontes de energia renovável, mas estas enfrentam desafios únicos. Gerir o excesso de energia produzido durante períodos de baixa procura e lidar com as limitações da actual tecnologia de baterias são obstáculos significativos. Além disso, a transmissão de energia a longas distâncias permanece ineficiente, o que impede que recursos renováveis remotos alcancem mercados mais amplos. Por exemplo, as linhas de corrente contínua de alta tensão (HVDC) perdem aproximadamente 3% de potência por cada 1.000 km, enquanto as linhas de corrente alternada de alta tensão (HVAC) perdem cerca de 7% por cada 1.000 km. Isto significa que, por cada quilómetro, as linhas HVDC perdem cerca de 0,003%, e as linhas HVAC perdem cerca de 0,007% (as linhas de alta tensão são projectadas para diminuir perdas, as perdas são ainda maiores na media tensão). Estas perdas, aliadas à dificuldade de transportar energia de parques renováveis remotos, sublinham a necessidade de soluções localizadas. Por exemplo, em 2018, cerca de 6,5 milhões de MWh de produção de energia solar fotovoltaica foram descartados, ou "mandados fora", no Chile, na China, na Alemanha e nos Estados Unidos conjuntamente. É importante notar que, à medida que a capacidade de energia renovável continua a crescer rapidamente (com o aumento das adições de capacidade renovável global anual em quase 50%, para quase 510 gigawatts em 2023), a quantidade absoluta de energia desperdiçada é susceptível de aumentar, a menos que se façam melhorias significativas na infraestrutura da rede, no armazenamento de energia e na gestão da procura. ### **Monetizar o Excesso de Energia através da Mineração de Bitcoin** Fontes de energia renovável, como a solar e a eólica, muitas vezes geram mais electricidade do que a rede necessita em determinados momentos, criando um excedente de energia que normalmente é desperdiçado. Este excesso permanece subutilizado porque: - As soluções de armazenamento em grande escala são limitadas e dispendiosas ou mesmo inexistentes; - A capacidade de transmissão muitas vezes não é suficiente para distribuir energia a longas distâncias; - E a procura nem sempre coincide com os períodos de produção máxima de energia renovável. A mineração de Bitcoin apresenta uma solução apelativa, ao actuar como um consumidor de energia flexível, capaz de ajustar rapidamente o seu consumo para se alinhar com a oferta. Operações de mineração localizadas perto de instalações de energia renovável — como centrais hidroeléctricas ou parques solares — podem absorver o excesso de energia que, de outra forma, seria desperdiçado, monetizando-o. Esta configuração não só reduz o desperdício de energia renovável, como também proporciona fontes de rendimento fiáveis para projectos renováveis, incentivando o investimento em infraestruturas verdes. #### **Mineração de Bitcoin como Consumidor Flexível** As operações de mineração de Bitcoin podem ajustar dinamicamente o seu consumo de energia, actuando como uma "carga flexível" na rede. As principais vantagens incluem: - **Escalabilidade Rápida**: Os equipamentos de mineração podem aumentar ou diminuir o seu consumo de energia quase instantaneamente, respondendo às flutuações na disponibilidade de energia. - **Independência Geográfica**: A mineração de Bitcoin pode ser realizada em qualquer local com ligação à internet, permitindo que os mineradores se situem perto das fontes renováveis, independentemente da infraestrutura da rede. - **Capacidade Modular**: O equipamento de mineração é altamente escalável, permitindo que os produtores de energia desenhem sistemas modulares que se adaptem à capacidade energética disponível. #### **Incentivos Económicos e Benefícios** A utilização do excedente de energia para a mineração de Bitcoin permite que os produtores de energia renovável gerem receitas a partir de energia que, de outra forma, seria desperdiçada. Este impulso económico aumenta a rentabilidade dos projectos de energia renovável, tornando-os mais atractivos para os investidores. Os benefícios adicionais incluem: - **Estabilização da Rede**: As operações de mineração ajudam a equilibrar a oferta e a procura na rede, contribuindo para a resiliência e estabilidade da mesma. - **Redução do Desperdício**: Ao consumir electricidade excedente, a mineração de Bitcoin reduz significativamente a quantidade de energia renovável desperdiçada. - **Aumento do Financiamento para Renováveis**: Os lucros provenientes da mineração de Bitcoin podem ser reinvestidos em novos projectos de energia renovável, soluções de armazenamento e infraestrutura de rede, criando um ciclo positivo de reforço para a energia verde. #### **Aplicações no Mundo Real** Vários exemplos ilustram como a mineração de Bitcoin monetiza eficazmente o excedente de energia: - No Texas, os mineradores de Bitcoin aproveitam o excesso de energia eólica, apoiando a rede através de programas de resposta à procura que aumentam a fiabilidade da rede durante períodos de alta e baixa procura. - No [Quebec](https://d-central.tech/the-untapped-potential-advocating-for-bitcoin-mining-as-a-key-to-quebecs-energy-future/), o excesso de energia hidroeléctrica é canalizado para operações de mineração de Bitcoin, o que ajuda a estabilizar a rede e a reduzir o desperdício de energia renovável. - Um [estudo](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development) da Universidade de Cornell descobriu que projectos de energia renovável nos EUA poderiam gerar milhões de dólares ao minerar Bitcoin durante estágios pré-comerciais, demonstrando a viabilidade económica desta abordagem. #### **Potencial Impacto na Transição para Energias Renováveis** Ao monetizar o excedente de energia através da mineração de Bitcoin, esta abordagem acelera a transição para energias renováveis. Os benefícios incluem: - **Viabilidade Económica para Renováveis**: A monetização da energia desperdiçada torna os projectos renováveis mais rentáveis e, portanto, mais atractivos para investidores. - **Flexibilidade da Rede**: A mineração de Bitcoin fornece uma fonte de procura escalável e adaptável, ajudando os operadores de rede a gerir as flutuações de oferta. - **Pegada de Carbono Reduzida**: Ao utilizar fontes renováveis, o impacto ambiental da mineração de Bitcoin diminui, alinhando-se com os objectivos de sustentabilidade. - **Adopção Acelerada de Energias Renováveis**: A maior rentabilidade e a redução do desperdício incentivam um maior investimento, impulsionando a adopção de tecnologias de energia renovável. Essencialmente, a mineração de Bitcoin oferece uma solução única para os desafios da produção intermitente de energia renovável, criando uma procura flexível e independente da localização para a electricidade excedente que, de outra forma, seria desperdiçada. À medida que mais projectos renováveis adoptam este modelo, a mineração de Bitcoin pode desempenhar um papel crucial na promoção de um panorama energético sustentável e descentralizado. ### **Fornecimento de Energia a Regiões Isoladas e Subdesenvolvidas** Um dos impactos mais promissores da mineração de Bitcoin é a capacidade de levar electricidade a regiões remotas e subdesenvolvidas. Pequenas centrais hidroeléctricas e instalações solares são opções cada vez mais viáveis para comunidades isoladas que não têm acesso a redes tradicionais. Mineradores de Bitcoin, em busca de energia barata e excedente, podem apoiar e financiar estas instalações, reduzindo a lacuna energética e permitindo o acesso a energia limpa para estas comunidades. Por exemplo, [aldeias](https://hackernoon.com/no-power-grid-this-african-village-mines-bitcoin-for-electricity) em África que anteriormente não tinham electricidade podem agora operar escolas, clínicas e empresas, graças a pequenos projectos de energia renovável apoiados pela mineração de Bitcoin. Este acesso catalisa o crescimento económico, criando um ciclo virtuoso onde a energia leva a investimentos, educação e melhor saúde — elevando comunidades inteiras para fora da pobreza. ### **Redução de Emissões através da Mitigação de Metano** A mineração de Bitcoin também contribui para a redução das emissões de metano — um gás de efeito estufa com um potencial de aquecimento global 28 a 34 vezes superior ao do CO₂ num período de 100 anos. As emissões de aterros sanitários, resíduos agrícolas e poços de petróleo abandonados representam uma ameaça climática significativa, mas a mineração de Bitcoin oferece uma solução única ao converter este poluente em energia. Quando o metano é queimado para gerar electricidade, é convertido em CO₂ e vapor de água, que, embora também sejam gases de efeito estufa, são muito menos potentes do que o metano. Na verdade, o metano é responsável por cerca de 25% do aquecimento global que experimentamos actualmente, apesar da sua concentração relativamente baixa na atmosfera. Ao capturar e utilizar o metano, as operações de mineração de Bitcoin transformam um dano ambiental numa fonte de energia produtiva, reduzindo as emissões globais de gases de efeito estufa e criando novas fontes de rendimento. Por exemplo, nos EUA, o metano de poços de petróleo abandonados está a ser capturado para alimentar a mineração de Bitcoin, criando um sistema fechado que evita que o metano seja queimado ou liberado directamente na atmosfera. Esta abordagem não só mitiga as emissões, como também apoia o crescimento económico em regiões com recursos de metano não aproveitados. ### **Resiliência e Flexibilidade da Rede** A integração de fontes renováveis, como a eólica e a solar, introduziu desafios para a estabilidade das redes eléctricas. Com as renováveis, os operadores de rede enfrentam flutuações de frequência mais frequentes e uma resposta inercial reduzida — as renováveis não fornecem a mesma resposta inercial que as centrais térmicas tradicionais, tornando a rede mais susceptível a mudanças rápidas. A flexibilidade da mineração de Bitcoin pode desempenhar um papel fundamental na estabilização das redes eléctricas. Durante a tempestade de inverno Uri, no Texas, os mineradores de Bitcoin reduziram o seu consumo de energia para libertar capacidade para serviços essenciais, mostrando o papel da mineração de Bitcoin como uma carga flexível e reactiva de energia. Ao ajustar o consumo de energia com base na disponibilidade de oferta, os mineradores de Bitcoin podem ajudar a equilibrar as redes com elevada penetração de renováveis. Esta sinergia com energias renováveis e nucleares fornece uma solução robusta para a gestão da procura energética, especialmente à medida que a rede transita para fontes de baixo carbono. ### **Impacto Ambiental de Longo Prazo** A mineração de Bitcoin tem o potencial de revolucionar a produção e o consumo de energia. Ao integrar energias renováveis, aproveitar o metano e oferecer gestão flexível da carga, o Bitcoin pode desempenhar um papel fundamental num futuro energético sustentável e descentralizado. Inovação política, responsabilidade industrial e colaboração intersectorial são essenciais para concretizar o potencial do Bitcoin na transição verde. Diante dos desafios ambientais actuais, a mineração de Bitcoin oferece mais do que inovação financeira. Representa um poderoso aliado na construção de um futuro sustentável e equitativo — onde os objectivos digitais e ambientais alinham-se para criar uma economia global mais limpa e resiliente. #Bitcoin #mining #greenEnergy #renewables --- _Photo by [Anders J]("https://unsplash.com/@aj5photos?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash") on [Unsplash]("https://unsplash.com/photos/white-and-blue-solar-panels-hxUcl0nUsIY?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_ @ 20986fb8:cdac21b3
2024-10-30 12:30:09**Hey Nostriches! ** Thrilled to launch the latest YakiHonne update—Simpler, Easier, Faster! After a lot of hard work, we bring you a highly optimized, user-friendly decentralized media experience on both web and mobile. This version focuses on two main aspects: **1. Complete Redesign:** Our UI/UX now puts simplicity first, minimizing technicalities for creators and social users alike. Here’s what’s new: • Onboarding: Easily create a non-custodial wallet with Npub & Nsec, experience zapping (Lightning payments), or browse as a guest. • Home & Discover: “Discover” is designed for creators, focusing on rich formats like long-form content, videos, and curated works. “Home” offers a social feed with short notes and curated contents, making it quick and easy for creators to share their work. • Wallet: Simple setup with easy creation, direct YakiHonne node linking, and multi-wallet support. • Dashboard: Manage all published and drafted content, check stats, and pick up right where you left off—all in one place. • Notifications: Reactions, Reposts, Mentions, Zaps, Comments, and Follows now appear in clear, categorized cards. • Settings: Completely revamped for simplicity, now including profile customization, appearance, relay settings, and wallet management. **2. Enhanced Performance:** Our re-engineered core now supports the outbox model with extensive functionality. Furthermore, Thanks to @PabloF7z we now have seamless data fetching, caching, and full support of the NDK implementation. Hope you enjoy the new decentralized media experience! 🌐✨Try it out here: **•Web**: yakihonne.com **•App Store (iOS)**: https://apps.apple.com/us/app/yakihonne/id6472556189 **•Google Play (Android)**: https://play.google.com/store/apps/details?id=com.yakihonne.yakihonne&hl=en Thank you for your incredible support on this decentralized media journey! https://v.nostr.build/Uu1uXf8P5D9KkBw6.mp4
@ 20986fb8:cdac21b3
2024-10-30 12:30:09**Hey Nostriches! ** Thrilled to launch the latest YakiHonne update—Simpler, Easier, Faster! After a lot of hard work, we bring you a highly optimized, user-friendly decentralized media experience on both web and mobile. This version focuses on two main aspects: **1. Complete Redesign:** Our UI/UX now puts simplicity first, minimizing technicalities for creators and social users alike. Here’s what’s new: • Onboarding: Easily create a non-custodial wallet with Npub & Nsec, experience zapping (Lightning payments), or browse as a guest. • Home & Discover: “Discover” is designed for creators, focusing on rich formats like long-form content, videos, and curated works. “Home” offers a social feed with short notes and curated contents, making it quick and easy for creators to share their work. • Wallet: Simple setup with easy creation, direct YakiHonne node linking, and multi-wallet support. • Dashboard: Manage all published and drafted content, check stats, and pick up right where you left off—all in one place. • Notifications: Reactions, Reposts, Mentions, Zaps, Comments, and Follows now appear in clear, categorized cards. • Settings: Completely revamped for simplicity, now including profile customization, appearance, relay settings, and wallet management. **2. Enhanced Performance:** Our re-engineered core now supports the outbox model with extensive functionality. Furthermore, Thanks to @PabloF7z we now have seamless data fetching, caching, and full support of the NDK implementation. Hope you enjoy the new decentralized media experience! 🌐✨Try it out here: **•Web**: yakihonne.com **•App Store (iOS)**: https://apps.apple.com/us/app/yakihonne/id6472556189 **•Google Play (Android)**: https://play.google.com/store/apps/details?id=com.yakihonne.yakihonne&hl=en Thank you for your incredible support on this decentralized media journey! https://v.nostr.build/Uu1uXf8P5D9KkBw6.mp4 @ 4c48cf05:07f52b80
2024-10-30 01:03:42> I believe that five years from now, access to artificial intelligence will be akin to what access to the Internet represents today. It will be the greatest differentiator between the haves and have nots. Unequal access to artificial intelligence will exacerbate societal inequalities and limit opportunities for those without access to it. Back in April, the AI Index Steering Committee at the Institute for Human-Centered AI from Stanford University released [The AI Index 2024 Annual Report](https://aiindex.stanford.edu/report/). Out of the extensive report (502 pages), I chose to focus on the chapter dedicated to Public Opinion. People involved with AI live in a bubble. We all know and understand AI and therefore assume that everyone else does. But, is that really the case once you step out of your regular circles in Seattle or Silicon Valley and hit Main Street? # Two thirds of global respondents have a good understanding of what AI is The exact number is 67%. My gut feeling is that this number is way too high to be realistic. At the same time, 63% of respondents are aware of ChatGPT so maybe people are confounding AI with ChatGPT? If so, there is so much more that they won't see coming. This number is important because you need to see every other questions and response of the survey through the lens of a respondent who believes to have a good understanding of what AI is. # A majority are nervous about AI products and services 52% of global respondents are nervous about products and services that use AI. Leading the pack are Australians at 69% and the least worried are Japanise at 23%. U.S.A. is up there at the top at 63%. Japan is truly an outlier, with most countries moving between 40% and 60%. # Personal data is the clear victim Exaclty half of the respondents believe that AI companies will protect their personal data. And the other half believes they won't. # Expected benefits Again a majority of people (57%) think that it will change how they do their jobs. As for impact on your life, top hitters are getting things done faster (54%) and more entertainment options (51%). The last one is a head scratcher for me. Are people looking forward to AI generated movies?  # Concerns Remember the 57% that thought that AI will change how they do their jobs? Well, it looks like 37% of them expect to lose it. Whether or not this is what will happen, that is a very high number of people who have a direct incentive to oppose AI. Other key concerns include: - Misuse for nefarious purposes: 49% - Violation of citizens' privacy: 45% # Conclusion This is the first time I come across this report and I wil make sure to follow future annual reports to see how these trends evolve. **Overall, people are worried about AI. There are many things that could go wrong and people perceive that both jobs and privacy are on the line.** --- Full citation: *Nestor Maslej, Loredana Fattorini, Raymond Perrault, Vanessa Parli, Anka Reuel, Erik Brynjolfsson, John Etchemendy, Katrina Ligett, Terah Lyons, James Manyika, Juan Carlos Niebles, Yoav Shoham, Russell Wald, and Jack Clark, “The AI Index 2024 Annual Report,” AI Index Steering Committee, Institute for Human-Centered AI, Stanford University, Stanford, CA, April 2024.* The AI Index 2024 Annual Report by Stanford University is licensed under [Attribution-NoDerivatives 4.0 International](https://creativecommons.org/licenses/by-nd/4.0/?ref=chooser-v1).
@ 4c48cf05:07f52b80
2024-10-30 01:03:42> I believe that five years from now, access to artificial intelligence will be akin to what access to the Internet represents today. It will be the greatest differentiator between the haves and have nots. Unequal access to artificial intelligence will exacerbate societal inequalities and limit opportunities for those without access to it. Back in April, the AI Index Steering Committee at the Institute for Human-Centered AI from Stanford University released [The AI Index 2024 Annual Report](https://aiindex.stanford.edu/report/). Out of the extensive report (502 pages), I chose to focus on the chapter dedicated to Public Opinion. People involved with AI live in a bubble. We all know and understand AI and therefore assume that everyone else does. But, is that really the case once you step out of your regular circles in Seattle or Silicon Valley and hit Main Street? # Two thirds of global respondents have a good understanding of what AI is The exact number is 67%. My gut feeling is that this number is way too high to be realistic. At the same time, 63% of respondents are aware of ChatGPT so maybe people are confounding AI with ChatGPT? If so, there is so much more that they won't see coming. This number is important because you need to see every other questions and response of the survey through the lens of a respondent who believes to have a good understanding of what AI is. # A majority are nervous about AI products and services 52% of global respondents are nervous about products and services that use AI. Leading the pack are Australians at 69% and the least worried are Japanise at 23%. U.S.A. is up there at the top at 63%. Japan is truly an outlier, with most countries moving between 40% and 60%. # Personal data is the clear victim Exaclty half of the respondents believe that AI companies will protect their personal data. And the other half believes they won't. # Expected benefits Again a majority of people (57%) think that it will change how they do their jobs. As for impact on your life, top hitters are getting things done faster (54%) and more entertainment options (51%). The last one is a head scratcher for me. Are people looking forward to AI generated movies?  # Concerns Remember the 57% that thought that AI will change how they do their jobs? Well, it looks like 37% of them expect to lose it. Whether or not this is what will happen, that is a very high number of people who have a direct incentive to oppose AI. Other key concerns include: - Misuse for nefarious purposes: 49% - Violation of citizens' privacy: 45% # Conclusion This is the first time I come across this report and I wil make sure to follow future annual reports to see how these trends evolve. **Overall, people are worried about AI. There are many things that could go wrong and people perceive that both jobs and privacy are on the line.** --- Full citation: *Nestor Maslej, Loredana Fattorini, Raymond Perrault, Vanessa Parli, Anka Reuel, Erik Brynjolfsson, John Etchemendy, Katrina Ligett, Terah Lyons, James Manyika, Juan Carlos Niebles, Yoav Shoham, Russell Wald, and Jack Clark, “The AI Index 2024 Annual Report,” AI Index Steering Committee, Institute for Human-Centered AI, Stanford University, Stanford, CA, April 2024.* The AI Index 2024 Annual Report by Stanford University is licensed under [Attribution-NoDerivatives 4.0 International](https://creativecommons.org/licenses/by-nd/4.0/?ref=chooser-v1). @ f462d21e:1390b6b1
2024-10-29 20:24:39eyJfaWQiOiJiMDYzYjQxMi04MGNmLTQxOTUtOTFhOS03MTM0MzExNDI4ZGIiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6IkNBU0hfQllfTUFJTCIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjo0LCJtYXJrZXRQcmljZSI6MTY0LjE4LCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwicGF5bWVudE1ldGhvZERldGFpbCI6ImZhc3QgcmVwbHkiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yOVQyMDoyNDozOS44NzRaIn0=
@ f462d21e:1390b6b1
2024-10-29 20:24:39eyJfaWQiOiJiMDYzYjQxMi04MGNmLTQxOTUtOTFhOS03MTM0MzExNDI4ZGIiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6IkNBU0hfQllfTUFJTCIsInByaWNlSW5wdXRUeXBlIjoiTUFSS0VUIiwibWFyZ2luIjo0LCJtYXJrZXRQcmljZSI6MTY0LjE4LCJmaXhlZFByaWNlIjowLCJtaW5BbW91bnQiOjAsIm1heEFtb3VudCI6MCwibGltaXRUb0ZpYXRBbW91bnRzIjoiIiwicGF5bWVudE1ldGhvZERldGFpbCI6ImZhc3QgcmVwbHkiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yOVQyMDoyNDozOS44NzRaIn0= @ 3f770d65:7a745b24
2024-10-29 17:38:20**Amber** [Amber](https://github.com/greenart7c3/Amber) is a Nostr event signer for Android that allows users to securely segregate their private key (nsec) within a single, dedicated application. Designed to function as a NIP-46 signing device, Amber ensures your smartphone can sign events without needing external servers or additional hardware, keeping your private key exposure to an absolute minimum. This approach aligns with the security rationale of NIP-46, which states that each additional system handling private keys increases potential vulnerability. With Amber, no longer do users need to enter their private key into various Nostr applications. <img src="https://cdn.satellite.earth/b42b649a16b8f51b48f482e304135ad325ec89386b5614433334431985d4d60d.jpg"> Amber is supported by a growing list of apps, including [Amethyst](https://www.amethyst.social/), [0xChat](https://0xchat.com/#/), [Voyage](https://github.com/dluvian/voyage), [Fountain](https://fountain.fm/), and [Pokey](https://github.com/KoalaSat/pokey), as well as any web application that supports NIP-46 NSEC bunkers, such as [Nostr Nests](https://nostrnests.com), [Coracle](https://coracle.social), [Nostrudel](https://nostrudel.ninja), and more. With expanding support, Amber provides an easy solution for secure Nostr key management across numerous platforms. <img src="https://cdn.satellite.earth/5b5d4fb9925fabb0005eafa291c47c33778840438438679dfad5662a00644c90.jpg"> Amber supports both native and web-based Nostr applications, aiming to eliminate the need for browser extensions or web servers. Key features include offline signing, multiple account support, and NIP-46 compatibility, and includes a simple UI for granular permissions management. Amber is designed to support signing events in the background, enhancing flexibility when you select the "remember my choice" option, eliminating the need to constantly be signing events for applications that you trust. You can download the app from it's [GitHub](https://github.com/greenart7c3/Amber) page, via [Obtainium ](https://github.com/ImranR98/Obtainium)or Zap.store. To log in with Amber, simply tap the "Login with Amber" button or icon in a supported application, or you can paste the NSEC bunker connection string directly into the login box. For example, use a connection string like this: bunker://npub1tj2dmc4udvgafxxxxxxxrtgne8j8l6rgrnaykzc8sys9mzfcz@relay.nsecbunker.com. <img src="https://cdn.satellite.earth/ca2156bfa084ee16dceea0739e671dd65c5f8d92d0688e6e59cc97faac199c3b.jpg"> --- **Citrine** [Citrine](https://github.com/greenart7c3/Citrine) is a Nostr relay built specifically for Android, allowing Nostr clients on Android devices to seamlessly send and receive events through a relay running directly on their smartphone. This mobile relay setup offers Nostr users enhanced flexibility, enabling them to manage, share, and back up all their Nostr data locally on their device. Citrine’s design supports independence and data security by keeping data accessible and under user control. <img src="https://cdn.satellite.earth/46bbc10ca2efb3ca430fcb07ec3fe6629efd7e065ac9740d6079e62296e39273.jpg"> With features tailored to give users greater command over their data, Citrine allows easy export and import of the database, restoration of contact lists in case of client malfunctions, and detailed relay management options like port configuration, custom icons, user management, and on-demand relay start/stop. Users can even activate TOR access, letting others connect securely to their Nostr relay directly on their phone. Future updates will include automatic broadcasting when the device reconnects to the internet, along with content resolver support to expand its functionality. Once you have your Citrine relay fully configured, simply add it to the Private and Local relay sections in Amethyst's relay configuration. <img src="https://cdn.satellite.earth/6ea01b68009b291770d5b11314ccb3d7ba05fe25cb783e6e1ea977bb21d55c09.jpg"> --- **Pokey** [Pokey](https://github.com/KoalaSat/pokey) for Android is a brand new, real-time notification tool for Nostr. Pokey allows users to receive live updates for their Nostr events and enabling other apps to access and interact with them. Designed for seamless integration within a user's Nostr relays, Pokey lets users stay informed of activity as it happens, with speed and the flexibility to manage which events trigger notifications on their mobile device. <img src="https://cdn.satellite.earth/62ec76cc36254176e63f97f646a33e2c7abd32e14226351fa0dd8684177b50a2.jpg"> Pokey currently supports connections with Amber, offering granular notification settings so users can tailor alerts to their preferences. Planned features include broadcasting events to other apps, authenticating to relays, built-in Tor support, multi-account handling, and InBox relay management. These upcoming additions aim to make Pokey a fantastic tool for Nostr notifications across the ecosystem. --- **Zap.store** [Zap.store](https://github.com/zapstore/zapstore/) is a permissionless app store powered by Nostr and your trusted social graph. Built to offer a decentralized approach to app recommendations, zap.store enables you to check if friends like Alice follow, endorse, or verify an app’s SHA256 hash. This trust-based, social proof model brings app discovery closer to real-world recommendations from friends and family, bypassing centralized app curation. Unlike conventional app stores and other third party app store solutions like Obtainium, zap.store empowers users to see which apps their contacts actively interact with, providing a higher level of confidence and transparency. <img src="https://cdn.satellite.earth/fd162229a404b317306916ae9f320a7280682431e933795f708d480e15affa23.jpg"> Currently available on Android, zap.store aims to expand to desktop, PWAs, and other platforms soon. You can get started by installing [Zap.store](https://github.com/zapstore/zapstore/) on your favorite Android device, and install all of the applications mentioned above. --- Android's openness goes hand in hand with Nostr's openness. Enjoy exploring both expanding ecosystems.
@ 3f770d65:7a745b24
2024-10-29 17:38:20**Amber** [Amber](https://github.com/greenart7c3/Amber) is a Nostr event signer for Android that allows users to securely segregate their private key (nsec) within a single, dedicated application. Designed to function as a NIP-46 signing device, Amber ensures your smartphone can sign events without needing external servers or additional hardware, keeping your private key exposure to an absolute minimum. This approach aligns with the security rationale of NIP-46, which states that each additional system handling private keys increases potential vulnerability. With Amber, no longer do users need to enter their private key into various Nostr applications. <img src="https://cdn.satellite.earth/b42b649a16b8f51b48f482e304135ad325ec89386b5614433334431985d4d60d.jpg"> Amber is supported by a growing list of apps, including [Amethyst](https://www.amethyst.social/), [0xChat](https://0xchat.com/#/), [Voyage](https://github.com/dluvian/voyage), [Fountain](https://fountain.fm/), and [Pokey](https://github.com/KoalaSat/pokey), as well as any web application that supports NIP-46 NSEC bunkers, such as [Nostr Nests](https://nostrnests.com), [Coracle](https://coracle.social), [Nostrudel](https://nostrudel.ninja), and more. With expanding support, Amber provides an easy solution for secure Nostr key management across numerous platforms. <img src="https://cdn.satellite.earth/5b5d4fb9925fabb0005eafa291c47c33778840438438679dfad5662a00644c90.jpg"> Amber supports both native and web-based Nostr applications, aiming to eliminate the need for browser extensions or web servers. Key features include offline signing, multiple account support, and NIP-46 compatibility, and includes a simple UI for granular permissions management. Amber is designed to support signing events in the background, enhancing flexibility when you select the "remember my choice" option, eliminating the need to constantly be signing events for applications that you trust. You can download the app from it's [GitHub](https://github.com/greenart7c3/Amber) page, via [Obtainium ](https://github.com/ImranR98/Obtainium)or Zap.store. To log in with Amber, simply tap the "Login with Amber" button or icon in a supported application, or you can paste the NSEC bunker connection string directly into the login box. For example, use a connection string like this: bunker://npub1tj2dmc4udvgafxxxxxxxrtgne8j8l6rgrnaykzc8sys9mzfcz@relay.nsecbunker.com. <img src="https://cdn.satellite.earth/ca2156bfa084ee16dceea0739e671dd65c5f8d92d0688e6e59cc97faac199c3b.jpg"> --- **Citrine** [Citrine](https://github.com/greenart7c3/Citrine) is a Nostr relay built specifically for Android, allowing Nostr clients on Android devices to seamlessly send and receive events through a relay running directly on their smartphone. This mobile relay setup offers Nostr users enhanced flexibility, enabling them to manage, share, and back up all their Nostr data locally on their device. Citrine’s design supports independence and data security by keeping data accessible and under user control. <img src="https://cdn.satellite.earth/46bbc10ca2efb3ca430fcb07ec3fe6629efd7e065ac9740d6079e62296e39273.jpg"> With features tailored to give users greater command over their data, Citrine allows easy export and import of the database, restoration of contact lists in case of client malfunctions, and detailed relay management options like port configuration, custom icons, user management, and on-demand relay start/stop. Users can even activate TOR access, letting others connect securely to their Nostr relay directly on their phone. Future updates will include automatic broadcasting when the device reconnects to the internet, along with content resolver support to expand its functionality. Once you have your Citrine relay fully configured, simply add it to the Private and Local relay sections in Amethyst's relay configuration. <img src="https://cdn.satellite.earth/6ea01b68009b291770d5b11314ccb3d7ba05fe25cb783e6e1ea977bb21d55c09.jpg"> --- **Pokey** [Pokey](https://github.com/KoalaSat/pokey) for Android is a brand new, real-time notification tool for Nostr. Pokey allows users to receive live updates for their Nostr events and enabling other apps to access and interact with them. Designed for seamless integration within a user's Nostr relays, Pokey lets users stay informed of activity as it happens, with speed and the flexibility to manage which events trigger notifications on their mobile device. <img src="https://cdn.satellite.earth/62ec76cc36254176e63f97f646a33e2c7abd32e14226351fa0dd8684177b50a2.jpg"> Pokey currently supports connections with Amber, offering granular notification settings so users can tailor alerts to their preferences. Planned features include broadcasting events to other apps, authenticating to relays, built-in Tor support, multi-account handling, and InBox relay management. These upcoming additions aim to make Pokey a fantastic tool for Nostr notifications across the ecosystem. --- **Zap.store** [Zap.store](https://github.com/zapstore/zapstore/) is a permissionless app store powered by Nostr and your trusted social graph. Built to offer a decentralized approach to app recommendations, zap.store enables you to check if friends like Alice follow, endorse, or verify an app’s SHA256 hash. This trust-based, social proof model brings app discovery closer to real-world recommendations from friends and family, bypassing centralized app curation. Unlike conventional app stores and other third party app store solutions like Obtainium, zap.store empowers users to see which apps their contacts actively interact with, providing a higher level of confidence and transparency. <img src="https://cdn.satellite.earth/fd162229a404b317306916ae9f320a7280682431e933795f708d480e15affa23.jpg"> Currently available on Android, zap.store aims to expand to desktop, PWAs, and other platforms soon. You can get started by installing [Zap.store](https://github.com/zapstore/zapstore/) on your favorite Android device, and install all of the applications mentioned above. --- Android's openness goes hand in hand with Nostr's openness. Enjoy exploring both expanding ecosystems. @ f462d21e:1390b6b1
2024-10-29 17:01:09eyJfaWQiOiJmOWQ2ZmEyOS1iNTI5LTQyMzktOTMyNS0xMzIzMjE0MzcxZWYiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwibWFya2V0UHJpY2UiOjE2NS4yOSwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjowLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yOVQxNzowMTowOS44NzRaIn0=
@ f462d21e:1390b6b1
2024-10-29 17:01:09eyJfaWQiOiJmOWQ2ZmEyOS1iNTI5LTQyMzktOTMyNS0xMzIzMjE0MzcxZWYiLCJwdWJsaWNLZXkiOiJmNDYyZDIxZTEwMTYzZWIwYTQwM2FlYzZiOTNhYzU3ZWMyZjFiOTQ1NTQ3M2U5OTMwNGY1NzFhNTEzOTBiNmIxIiwiYWRUeXBlIjoiT05MSU5FX1NFTEwiLCJjb3VudHJ5IjoiVW5pdGVkIFN0YXRlcyBvZiBBbWVyaWNhIiwiY291bnRyeUNvZGUiOiJVUyIsImxhdCI6bnVsbCwibG9uIjpudWxsLCJjdXJyZW5jeUNvZGUiOiJVU0QiLCJwYXltZW50TWV0aG9kQ29kZSI6Ik5BVElPTkFMX0JBTksiLCJwcmljZUlucHV0VHlwZSI6Ik1BUktFVCIsIm1hcmdpbiI6MCwibWFya2V0UHJpY2UiOjE2NS4yOSwiZml4ZWRQcmljZSI6MCwibWluQW1vdW50IjowLCJtYXhBbW91bnQiOjAsImxpbWl0VG9GaWF0QW1vdW50cyI6IiIsInBheW1lbnRNZXRob2REZXRhaWwiOiIiLCJtc2ciOiIiLCJhY2NvdW50SW5mbyI6IiIsImZvclRydXN0ZWQiOiJubyIsInZlcmlmaWVkRW1haWxSZXF1aXJlZCI6Im5vIiwicmVxdWlyZUZlZWRiYWNrU2NvcmUiOjAsImZpcnN0VGltZUxpbWl0QXNzZXQiOjAsInBheW1lbnRXaW5kb3dNaW51dGVzIjo2MCwiaGlkZGVuIjpmYWxzZSwiYmFubmVkIjpmYWxzZSwidmVyaWZpZWQiOnRydWUsImFkZGVkIjoiMjAyNC0xMC0yOVQxNzowMTowOS44NzRaIn0= @ 4ba8e86d:89d32de4
2024-10-29 12:30:05## Tutorial feito por Grom Mestre⚡ Poste original Abaixo. Part 1: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/229987/tutorial-entendendo-e-usando-a-rede-i2p-introdu%C3%A7 Part 2: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/230035/tutorial-instalando-e-configurando-o-roteador-i2p?show=230035#q230035 Part 3: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/230113/tutorial-conectando-se-ao-xmpp-pela-i2p?show=230113#q230113 Boa tarde, camaradas do meu coeur! Depois de muito tempo, e com o retorno da minha serotonina aos níveis basais, estou dando início a essa nova série de tutoriais. Espero que tirem muito proveito das informações passadas aqui para amplicarem o seu conhecimento da deepweb. Esta postagem trará antes algumas considerações iniciais que podem ser úteis para quem possui pouco ou nenhum contato prévio com outras tecnologias ou tenha um entendimento torto a respeito da deepweb. Aconselho a estes que deem um boa lida antes de partirem para os tópicos do tutorial, mas saibam que ele não é um pré requisito para ele. Dito isso, vamos prosseguir. TÓPICOS: Introdução Instalando e configurando o roteador e o navegador Conectando-se a serviços na I2P Configurações avançadas ## 1. Introdução ### 1.1 Definindo a DeepWeb. Muitos devem imaginar erroneamente que a deepweb se restrinja apenas à rede onion, mais precisamente aos seus hidden services, já que o Tor possui como uma das suas funções primárias proteger e burlar restrições governamentais e proteger o seus usuários através de métodos sofisticados de roteamento de pacotes e criptografia. Entretanto, ela é mais ampla do que se imagina dependendo da forma como a classificamos. Os ditos "profissionais" usam uma definição extremamente vaga e imprecisa do que seria a deepweb e a sua verdadeira abrangência. Para isso, criei uma definição um pouco melhor para ela: redes comunitárias, sobrepostas, anônimas e criptografadas. Vamos aos pontos individualmente: > São Comunitárias, pois os pontos de roteamento de pacotes na rede (relays ou routers) muitas vezes são mantidos de forma voluntária por usuários comuns. Não é necessário nenhuma infraestrutura sofisticada para ser um contribuinte na rede, basta ter um computador com acesso à internet e conhecimentos básicos para fazer a configuração. > São sobrepostas porque não estão acima ou abaixo da rede tradicional (diferente do que muitos imaginam). Os pacotes na DW trafegam entre os dados da surface e não em meios distintos (algo que não faz o menor sentido). Sabe aquele papo de camadas da DW ou aquela abobrinha da Mariana's Web? Então, tudo um monte de bosta derivado de Youtubers sensacionalistas iletrados em informática. Elitismo da minha parte? Quem sabe... > São anônimas porque não é simples determinar a origem e o destino dos pacotes entre nodes intermediários dado a natureza do roteamento. Em geral, aos menos para a rede onion, há pelo menos 3 relays entre você e o servidor, sendo que esse número duplica para hidden services (3 seus e 3 do serviço). A imagem abaixo ilustra bemocoteamento dos pacotes na onio. https://image.nostr.build/aea96f41d356157512f26b479ea8db5bce8693dd642f2bce0258d8e4b0dac053.jpg > Por fim, são criptografadas porque as conexões são fortemente protegidas por algoritmos sofisticados de criptografia. Além de não sabermos a origem dos dados, sequer podemos saber com facilidade o conteúdo dessas mensagens mesmo que os protocolos das camadas superiores (HTTP, HTTPS, FTP) sejam inseguros, dado que a criptografia da própria rede já as protege. Por isso é tão comum que sites da DW não usem HTTPS, pois as autoridades de certificados não os assinam para domínios da onion e certificados autoassinados vão disparar avisos no navegador. A imagem abaixo ilustra bem como é o roteamento onion usado pelo Tor. Perceba que o contéudo da mensagem está enrolado em 3 camadas de criptografia (como a de uma cebola), de modo que para revelar o contéudo original seria preciso quebrar, no pior dos casos, 3 camadas. Como mencionado antes, o método usado para isso é a criptografia assimétrica, muito similar ao PGP, porém com a sua própria implementação. https://image.nostr.build/7bfaaf29211c11b82049ef8425abb67738d085c41558e9339ec13cf49ea5b548.jpg Observação: Por mais que dentro da rede o encapsulamento proteja as mensagens internamente, entenda muito bem que isso não se aplica a sites da surface acessados pela onion. Ao desempacotar a última camada, a mensagem original é completamente exposta no exit node. Se ela não estiver protegida por uma camada adicional como TLS, seus pacotes estarão completamente expostos, algo que representa um sério risco de segurança. As redes que caem em ao menos três dessas definições (anonimato, sobreposição e criptografia) podem ser classificadas como deepwebs. Podemos citar: • Lokinet • Zeronet • Freenet • I2P • Tor • Gnunet Porém, há alguns casos interessantes que não caem diretamente nessa regra . A Yggdrasil ( https://yggdrasil-network.github.io/ ), uma rede de topologia mesh com foco em escalabilidade e eficiência de roteamento, possui três dessas características: comunitária, sobreposta e segura. Entretanto, os nodes não são anônimos e muitas vezes podem estar desprotegidos, já que se conectar à Yggdrasil é que equivalente a ligar o seu computador diretamente na rede sem a presença de um NAT/CGNAT, correndo o risco de expor portas de serviços da sua máquina caso elas não estejam protegidas por um firewall. A Yggdrasil na prática é exposta como um dispositivo de camada 3 (tipo um VPN), mas diferente de um, apenas endereços IPv6 dentro de uma faixa bem específica de IP são roteados por ela, o que permite que ela coexista com outros dispositivos sem haver conflitos de roteamento. Há quem argumente que a Yggdrasil é uma deepweb dado a sua sobreposição em relação à surface; outros podem argumentar que dado a falta de anonimato ela não se enquadraria nessa categoria. Independentemente disso é uma tecnologia muito interessante com ampla gama de aplicações, como encapsular tráfego de outras redes, como a I2P, e melhorar a eficiência de roteamento. Por fim, vamos desmitificar alguns mitos da DeepWeb muito difundidos. Não existem camadas da DW. Os pacotes da DW são sobrepostos e navegam juntos aos pacotes da surface. DeepWeb e DarkWeb não são coisas diferentes. São termos genéricos para a mesma coisa. DarkWeb não é o seu provedor de e-mail ou serviço de banco. Se eles não se enquadram nas categorias de um deepweb, então estão na surface. Você não é irrastreável na DW. Adversários motivados podem foder com você com facilidade (leia a respeito de ataques de Timing, correlação e fingerprinting). Mesmo que não seja possível ver o conteúdo de uma mensagem pela deepweb, é possível ao menos saber que você a acessou. ISPs podem ver esse tipo de tráfego como suspeito. Você não é um hacker só porque instalou o TorBrowser, mas pode ser considerado um se expor o IP de um hidden service. ## Instalando e configurando o roteador I2P Segue agora a seção 2 do tutorial do I2P. Mas antes apenas queria falar um pouco do projeto I2P. Apesar do foco do tutorial não ser para tratar da sua história, gostaria ao menos de fazer uma breve introdução sobre ela. O projeto I2P (Invisible Internet Protocol) é uma rede P2P descentalizada, anônima e segura para estabelecer a comunicação entre os usuários e serviços. Na I2P é possível usar serviços como mensageiros IRC, XMPP, web services, e-mail e até mesmo torrents. A I2P nasceu de um fork da Freenet no ano de 2003, porém possui diferenças drásticas em relação a ela. Há similaridades entre a I2P e o Tor, porém vale destacar algumas de suas vantagens. Sendo elas: • Garlic routing ( https://geti2p.net/en/docs/how/garlic-routing ) • Modelo P2P • Todos os participantes da rede contribuem para ela • Fechado na rede - não é possível acessar a surface através da I2P • Otimizado para hidden services Apesar disso, vale lembrar que o projeto é pequeno, desenvolvido por menos voluntários se comparado ao Tor e possui menos movimentação e financiamento para o seu desenvolvimento. Além disso, o Tor é um projeto muito mais maduro e bem documentado, algo que atrai mais usuários e desenvolvedores e torna a tarefa de encontrar e corrigir bugs mais fácil de ser realizada. Esses são pontos importantes que devemos levar em conta ao escolher a tecnologia para as nossas necessidades. Nem sempre há tecnologias ruins, as vezes apenas as empregamos as ferramentas erradas na resolução de certos problemas. Referências: • https://geti2p.net/en/comparison/tor • https://geti2p.net/en/docs/how/garlic-routing • https://geti2p.net/en/about/intro • https://i2pd.readthedocs.io/en/latest/ ### 2. Instalando e configurando o roteador Antes da criação do I2PBrowserBundle ( https://github.com/PurpleI2P/i2pdbrowser/releases/tag/1.3.3 ) , a única forma de se conectar à I2P era pela configuração manual de proxy no navegador. Muita gente ou não sabe ou tem MUUUUUITA preguiça de fazer isso e ficam resistentes de entrar na I2P dada essa restrição. Como eu quero ser um bom tutor eu farei do jeito mais "difícil", pois tanto eu desejo que vocês aprendam as nuances do processo como eu sei que vocês são inteligentes o suficiente para fazer isso. ### 2.1 Instalação do router Atualmente nós temos duas implementações do I2P: Uma em Java e outra em C++ (i2pd). Usaremos nesse tutorial a versão em C++ dado o seu baixo uso de recursos e facilidade de instalação. O I2Pd está disponível para Windows, Linux, MacOS e Android e possui binários pré-compilados nas releases ( https://github.com/PurpleI2P/i2pd/releases/tag/2.50.2 ) do projeto no Github. Usuários de Linux podem instalá-lo através do respectivo gerenciador de pacotes da sua distribuição, porém algumas distros não oferecem o pacote diretamente nos reposítórios oficiais, necessitando do uso de PPAs (Ubuntu), COPR (Fedora/RHEL) e afins. Vocês podem conferir as instruções oficiais para cada sistema nessa página ( https://i2pd.readthedocs.io/en/latest/user-guide/install/ ). Apesar desse tutorial ser voltado a usuários de desktop, o I2Pd também está disponível na loja do F-droid. Infelizmente poucos navegadores em Android permitem a configuração de proxies, porém na seção de Serviços na I2P eu tratarei brevemente de como se conectar a servidores de XMPP usando o ConversationI2P. Para usuários de Windows, segue abaixo os binários para instalação. • Versão 32bits ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_win32_mingw.zip ) • Versão 64bits ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_win64_mingw.zip ) • Versão para Windows XP (pois é, kk) ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_winxp_mingw.zip ) A instalação é simples e direta. Após ela apenas abram o I2Pd para que o router inicie a operação de busca e conexão com os peers. Para usuários de Linux, vocês precisam ativar o serviços através do comando 'sudo systemctl start i2pd'. Se vocês desejam que o I2Pd inicie junto com o sistema usem o comando 'sudo systemctl enable --now i2pd'. Se tudo estiver funcionando corretamente, vocês serão capazes de abrir o webconsole do I2Pd no navegador através do endereço: 127.0.0.1:7070. https://image.nostr.build/ab205ae1071a2b705279e5ce2d6e912d8d11cc7d6dd0dc8a26b76724a27bd94b.jpg https://image.nostr.build/fa17e14600737ccfc92a415cec2fbfba226b950b2b97af7475927ae65abdbe11.jpg ### 2.2 Instalação e configuração do navegador Apesar de qualquer navegador ser capaz de usar a I2P não é recomendado que usem qualquer um, especialmente o navegador que você usam no seu dia-a-dia. Recomendo que usem um navegador próprio para usar na I2P ou isolem suas atividades em um perfil separado. Em navegadores baseado no Firefox isso é relativamente simples, bastando adicionar a opção '--profile' e o caminho do perfil que vocês desejam usar. Nesse tutorial eu vou mostrar como criar um perfil novo no Librewolf e configurar no lançador para iniciar o perfil e abrir em uma janela anônima. Essas instruções são análogas para todos os sistemas, excetuando aquelas configurações mais exóticas. ### 2.2.1 Escolhendo o navegador Como citado, usarei o Librewolf como exemplo. Vocês podem baixar o instalador direto do site ou usar o gerenciador de pacotes do seu sistema no caso de Linux. Como é uma tarefa trivial eu não vou detalhar esse processo, pois todas as instruções estão em detalhes no site do navegador ( https://librewolf.net/installation/ ) ### 2.2.2 Criando um perfil e configurando o lançador Abram o navegador e digitem 'about:profiles' na barra de endereço. Criem um novo perfil clicando em 'Create New Profile' https://image.nostr.build/fa17e14600737ccfc92a415cec2fbfba226b950b2b97af7475927ae65abdbe11.jpg Coloquem um nome no seu perfil e cliquem em Finalizar https://image.nostr.build/62059e375000940f11b27ae77b9ec011f9baadbb5a84afc910d41841ce73e82d.jpg Perfis novos recém criados são iniciados por padrão. Se você deseja usar outro perfil por padrão deve mudar isso na seção 'about:profiles' do navegador. Agora vamos configurar o lançador do LibreWolf para iniciar o perfil do i2p e em uma janela anônima. Usarei o XFCE como referência para essa tarefa, mas saibam que o processo é análogo em sistemas como Windows ou DEs como KDE. Se quiserem também podem lançar via terminal através do comando 'librewolf --profile caminho_do_perfil --private-window'. Cliquem com o botão direito no ícone do Librewolf e abram as propriedades do atalho. Na guia lançador, no campo Comando, adicionem no final a opção '--private-window' e a opção '--profile caminho_do_perfil'. O caminho do perfil é aquele mostrado na seção 'about:profiles' do Librewolf. https://image.nostr.build/a7d6515d7825cb3bdcb681ecf71a97318dccba81eea7cc87fc5377ecc06065ee.jpg 2.2.3 Configurando o proxy Com o lançador configurado, abra o navegador nesse perfil. Vamos configurar o proxy para se conectar ao I2P agora. Abra as configurações digitando 'about:preferences' na barra de endereço. Na seção 'Geral' abra as configurações de rede (Network Settings) https://image.nostr.build/f37157bebf15ada616914f403e756cf9fcee4c9aaaa353196c9cc754ca4d7bc5.jpg Configure o seu proxy como na figura abaixo. https://image.nostr.build/41ebd05255a8129d21011518d400689308d9c0320408967003bf296771e0b96f.jpg Fecha as configurações. Se o seu proxy foi configurado corretamente tente abrir algum desses eepsites. • http://identiguy.i2p • http://notbob.i2p • http://reg.i2p Se tudo ocorreu como conforme, a página será carregada. https://image.nostr.build/ce29ae44743f06cfed591f082208c9612c59b3429ab46d90db48131b3bc3e99d.jpg OBSERVAÇÃO: A busca pelos peers é um pouco demorada, levando de 2 a 5 minutos para que um número mínimo necessário de peers sejam encontrados para estabelecer uma conexão estável. Você pode ver a lista de inbound e outbound tunnels na seção Tunnels do WebConsole (localhost:7070) https://image.nostr.build/285a0d765eaf5f33409f975cd720d0efa68ecc40a9da20bfd9cde0cd1f59a7b6.jpg IMPORTANTE: Apesar do Librewolf possuir defaults seguros, eu recomendo que vocês instalem as seguintes extensões para aumentar ainda mais a sua proteção. • noScript • JShelter Lembrem-se que vocês precisam desativar o proxy para acessar a clearnet. Depois disso reativem-no nas configurações. Outro detalhe: Se vocês tentarem digitar um endereço .i2p na barra de endereços do navegador sem especificar o protocolo (http), ao invés do Librewolf ir ao endereço ele vai realizar uma pesquisa. Para corrigir esse problema, vocês precisam adicionar a seguinte configuração do tipo boolean em 'about:config' como mostrado na imagem. https://image.nostr.build/4518ab817b131f7efe542b2d919b926099dce29a7b59bdd3c788caf53dbd071e.jpg Reiniciem o navegador e testem. Se tudo deu certo vocês não precisam especificar o protocolo ao digitar um endereço .i2p, bastando apenas digitar o endereço simplificado. Por fim, terminamos essa parte do tutorial. Na próximo parte trataremos de como podemos nos conectar a serviços hospedados na I2P como XMPP ## [TUTORIAL] Conectando-se ao XMPP pela I2P Essa é a terceira parte da série de tutoriais. Agora vamos tratar de algumas operações na rede, sendo uma delas conectando-se a um servidor de XMPP na I2P. Não se esqueça de ligar o router e manter ele ligado por alguns minutos antes de iniciar essas operações. O router demora um pouco para encontrar os peers e estabelecer uma conexão estável. ### 3.1 Escolhendo o cliente XMPP Existem diversos clientes XMPP capazes de se conectar usando um proxy. Um dos melhores é o Gajim, um cliente escrito em Python com diversas funcionalidades como criptografia OMEMO e PGP, workspaces separados, extensibilidade via plugins e uma interface bonita e organizada. Assim como ocorreu com o router, o Gajim está disponível por padrão na maioria das distros Linux. Use o seu gerenciador de pacotes para instala-lo. Em Windows você pode baixar o Gajim através desse link ( https://gajim.org/download/ ) ### 3.2 Criando uma conta Vamos primeiro criar uma conta no servidor. No nosso exemplo usarei o servidor oficial do projeto i2pd, o xmpp.ilita.i2p. Há diversos outros servidores XMPP no diretório de links notbob.i2p caso queiram explorar mais. Para criar uma conta, siga os passos abaixo: Abra o Gajim. Na barra de tarefas vá em Contas -> Adicionar Conta. Na nova janela que aparecer, clique em Adicionar Conta https://image.nostr.build/01413e7c6d00c238420e3b0c769dd8d7f7d6522754d2135d3e98a22944f79a27.jpg https://image.nostr.build/9f015861f33990871d96f03d5ec78036a65e3ad9f8ff6a38da18c5b27d31f6d5.jpg Na janela de adicionar contas, clique diretamente em Inscrever-se. Não precisa colocar as suas credencias como mostra a imagem (falha minha, ksksk) https://nostrcheck.me/media/c8411a22946e97467e0ee197ef7a0205ba05f2c67bde092041481ccc2cbbc66d/81938c8d278ce0562c2240341e203f3b70f51ee2db06ceb453f8a178df37fa84.webp Digite o nome do servidor no campo abaixo. Não esqueça de marcar a opção 'Configurações Avançadas' antes de clicar em Inscrever-se https://image.nostr.build/5ee4305a6a23e5c064446b0ce7a4cbc7e790c1ba237bd2495d0237b86a4df07f.jpg Vamos adicionar um novo proxy para essa conta. Para isso clique no botão 'Gerenciar proxies', ao lado do campo Proxy nas Configurações Avançadas https://image.nostr.build/daceb5436def55401d3974ce48d85771e5ebcec4e3f90eb1001df4609112ec12.jpg Adicione um novo proxy clicando no sinal de '+' abaixo da lista de proxies. Preencha os campos de acordo com a imagem abaixo e em seguida feche a janela. https://image.nostr.build/140b34c4e46e9295c073311d483d206201d9339a75f613fe4e829c14f3257bfe.jpg https://image.nostr.build/d365a63d81a14d763bffceb50b30eb53d81959623f8fe812175358a41b1fba53.jpg No campo de Proxy, selecione o proxy I2P. Preencha o restante dos campos de acordo com a imagem abaixo. Em seguida clique em 'Inscrever-se'. https://image.nostr.build/d06c11d9c6d19728bf5a58af2dd3e14d8ca0021456da09792a345ac0bfc90ad0.jpg Nesse momento uma mensagem pode aparecer pedindo para abrir uma exceção para o certificado TLS. Isso acontece porque trata-se de um certificado autoassinado que não foi validado por uma autoridade oficial. Apenas abra a exceção e prossiga (não há imagem para isso porque eu já abri essa exceção no meu cliente). Uma nova janela vai aparecer solicitando-lhe para inserir as suas credenciais. Tome cuidado aqui, pois não é para inserir o nome completo com o domínio, apenas o seu nome de usuário (ex: descartavel). https://image.nostr.build/dde2a6736bd00080fbeeb8076754e226971a412710b370d5559f7f4d5414f8b3.jpg Se tudo der certo, uma nova janela vai aparecer confirmando a sua inscrição. Coloque um nome e uma cor para a sua conta e clique em Conectar para concluir o processo. https://image.nostr.build/74934d3f1f3f4232eacee8e78e707936227f816c50ac6b52da5c81ec17557e69.jpg Para finalizar, nos detalhes da sua conta, modifique as suas configurações de privacidade para diminuir o fingerprint. Na seção de 'Privacidade', desligue as seguintes opções: • Tempo ocioso • Hora de Sistema Local • Sistema Operacional • Reprodução de Mídia https://image.nostr.build/d2ed5852a104c770b50c7b053d518d8af0b6289ced6b3ad4187492208c7ca649.jpg ### 3.3 Procurando por salas de bate-papo públicas Após criar a sua nova conta, vamos descobrir alguns serviços que o servidor oferece. Para isso, vá para Contas -> Descobrir serviços https://image.nostr.build/54928d1dd0e48365858b24c72097a9fabf677794e13f329fc0568211eefbe559.jpg Na seção 'Bate-papo em Grupo', selecione Chatrooms e clique em 'Navegar'. Ao fazer isso uma lista de chatroom públicos presentes no servidor vai aparecer. Fique a vontade para explorar, porém saiba que alguns servidores são moderados e não te permitem mandar mensagens sem sua conta ser aprovada pelo moderador (familiar?). https://image.nostr.build/1936bef51d58a1f6cfdf8bf8d84bfa64adc2a09b9c0fb1623b93a327f0b8cdd8.jpg https://image.nostr.build/89e8013b1cea1df0f80f6833bd6771c33101f404b0099b2d7330a5e57607baff.jpg ### 3.4 Adicionando contatos Para adicionar contatos à sua lista, clique no símbolo de '+' ao lado do campo de pesquisa e selecione 'Add Contact'. https://image.nostr.build/d3cadea27591355f674fba93765c3815282d112b2e80a592bb77a442c13dd4f4.jpg Coloque o endereço completo da conta que você deseja adicionar. Usarei a minha conta oficial nesse exemplo. Você tem a opção de anexar uma mensagem qualquer antes de enviar o convite. Clique em 'Adicionar Contato' para prosseguir. https://image.nostr.build/ff95b7aec2377c58d4253c5b7b3aabf141a92dd5f3e97f6e1f01ecb32a215d38.jpg https://image.nostr.build/6562e680e28c321ebbd009b5ade513f8a279aea33bc16aa9fb251f3507eb04af.jpg Se tudo ocorrer normalmente, o novo contato vai aparecer na sua lista. Dê dois-cliques na conta para abrir o chat. Não se esqueça de ativar a criptografia OMEMO antes de enviar qualquer mensagem. Agora você está pronto para conversar de forma segura :) https://image.nostr.build/ef7f783a311ad0f68a5408137f75dc2bc6c38f6e9656dc0d68d3267f5012f658.jpg E com isso terminamos a terceira parte da série de tutoriais. ## [TUTORIAL] Criando e conectando-se a um servidor XMPP na I2P e clearnet. Como configurar o seu próprio servidor XMPP. https://youtube.com/watch?v=Ot_EmQ8xdJwy Criando contas e conectando clientes Pidgin http://i2pd.readthedocs.io/en/latest/tutorials/xmpp/#creating-accounts-and-connecting-clients BONUS: Conectando-se facilmente à I2P. https://youtube.com/watch?v=wGIh5tQcw68
@ 4ba8e86d:89d32de4
2024-10-29 12:30:05## Tutorial feito por Grom Mestre⚡ Poste original Abaixo. Part 1: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/229987/tutorial-entendendo-e-usando-a-rede-i2p-introdu%C3%A7 Part 2: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/230035/tutorial-instalando-e-configurando-o-roteador-i2p?show=230035#q230035 Part 3: http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/230113/tutorial-conectando-se-ao-xmpp-pela-i2p?show=230113#q230113 Boa tarde, camaradas do meu coeur! Depois de muito tempo, e com o retorno da minha serotonina aos níveis basais, estou dando início a essa nova série de tutoriais. Espero que tirem muito proveito das informações passadas aqui para amplicarem o seu conhecimento da deepweb. Esta postagem trará antes algumas considerações iniciais que podem ser úteis para quem possui pouco ou nenhum contato prévio com outras tecnologias ou tenha um entendimento torto a respeito da deepweb. Aconselho a estes que deem um boa lida antes de partirem para os tópicos do tutorial, mas saibam que ele não é um pré requisito para ele. Dito isso, vamos prosseguir. TÓPICOS: Introdução Instalando e configurando o roteador e o navegador Conectando-se a serviços na I2P Configurações avançadas ## 1. Introdução ### 1.1 Definindo a DeepWeb. Muitos devem imaginar erroneamente que a deepweb se restrinja apenas à rede onion, mais precisamente aos seus hidden services, já que o Tor possui como uma das suas funções primárias proteger e burlar restrições governamentais e proteger o seus usuários através de métodos sofisticados de roteamento de pacotes e criptografia. Entretanto, ela é mais ampla do que se imagina dependendo da forma como a classificamos. Os ditos "profissionais" usam uma definição extremamente vaga e imprecisa do que seria a deepweb e a sua verdadeira abrangência. Para isso, criei uma definição um pouco melhor para ela: redes comunitárias, sobrepostas, anônimas e criptografadas. Vamos aos pontos individualmente: > São Comunitárias, pois os pontos de roteamento de pacotes na rede (relays ou routers) muitas vezes são mantidos de forma voluntária por usuários comuns. Não é necessário nenhuma infraestrutura sofisticada para ser um contribuinte na rede, basta ter um computador com acesso à internet e conhecimentos básicos para fazer a configuração. > São sobrepostas porque não estão acima ou abaixo da rede tradicional (diferente do que muitos imaginam). Os pacotes na DW trafegam entre os dados da surface e não em meios distintos (algo que não faz o menor sentido). Sabe aquele papo de camadas da DW ou aquela abobrinha da Mariana's Web? Então, tudo um monte de bosta derivado de Youtubers sensacionalistas iletrados em informática. Elitismo da minha parte? Quem sabe... > São anônimas porque não é simples determinar a origem e o destino dos pacotes entre nodes intermediários dado a natureza do roteamento. Em geral, aos menos para a rede onion, há pelo menos 3 relays entre você e o servidor, sendo que esse número duplica para hidden services (3 seus e 3 do serviço). A imagem abaixo ilustra bemocoteamento dos pacotes na onio. https://image.nostr.build/aea96f41d356157512f26b479ea8db5bce8693dd642f2bce0258d8e4b0dac053.jpg > Por fim, são criptografadas porque as conexões são fortemente protegidas por algoritmos sofisticados de criptografia. Além de não sabermos a origem dos dados, sequer podemos saber com facilidade o conteúdo dessas mensagens mesmo que os protocolos das camadas superiores (HTTP, HTTPS, FTP) sejam inseguros, dado que a criptografia da própria rede já as protege. Por isso é tão comum que sites da DW não usem HTTPS, pois as autoridades de certificados não os assinam para domínios da onion e certificados autoassinados vão disparar avisos no navegador. A imagem abaixo ilustra bem como é o roteamento onion usado pelo Tor. Perceba que o contéudo da mensagem está enrolado em 3 camadas de criptografia (como a de uma cebola), de modo que para revelar o contéudo original seria preciso quebrar, no pior dos casos, 3 camadas. Como mencionado antes, o método usado para isso é a criptografia assimétrica, muito similar ao PGP, porém com a sua própria implementação. https://image.nostr.build/7bfaaf29211c11b82049ef8425abb67738d085c41558e9339ec13cf49ea5b548.jpg Observação: Por mais que dentro da rede o encapsulamento proteja as mensagens internamente, entenda muito bem que isso não se aplica a sites da surface acessados pela onion. Ao desempacotar a última camada, a mensagem original é completamente exposta no exit node. Se ela não estiver protegida por uma camada adicional como TLS, seus pacotes estarão completamente expostos, algo que representa um sério risco de segurança. As redes que caem em ao menos três dessas definições (anonimato, sobreposição e criptografia) podem ser classificadas como deepwebs. Podemos citar: • Lokinet • Zeronet • Freenet • I2P • Tor • Gnunet Porém, há alguns casos interessantes que não caem diretamente nessa regra . A Yggdrasil ( https://yggdrasil-network.github.io/ ), uma rede de topologia mesh com foco em escalabilidade e eficiência de roteamento, possui três dessas características: comunitária, sobreposta e segura. Entretanto, os nodes não são anônimos e muitas vezes podem estar desprotegidos, já que se conectar à Yggdrasil é que equivalente a ligar o seu computador diretamente na rede sem a presença de um NAT/CGNAT, correndo o risco de expor portas de serviços da sua máquina caso elas não estejam protegidas por um firewall. A Yggdrasil na prática é exposta como um dispositivo de camada 3 (tipo um VPN), mas diferente de um, apenas endereços IPv6 dentro de uma faixa bem específica de IP são roteados por ela, o que permite que ela coexista com outros dispositivos sem haver conflitos de roteamento. Há quem argumente que a Yggdrasil é uma deepweb dado a sua sobreposição em relação à surface; outros podem argumentar que dado a falta de anonimato ela não se enquadraria nessa categoria. Independentemente disso é uma tecnologia muito interessante com ampla gama de aplicações, como encapsular tráfego de outras redes, como a I2P, e melhorar a eficiência de roteamento. Por fim, vamos desmitificar alguns mitos da DeepWeb muito difundidos. Não existem camadas da DW. Os pacotes da DW são sobrepostos e navegam juntos aos pacotes da surface. DeepWeb e DarkWeb não são coisas diferentes. São termos genéricos para a mesma coisa. DarkWeb não é o seu provedor de e-mail ou serviço de banco. Se eles não se enquadram nas categorias de um deepweb, então estão na surface. Você não é irrastreável na DW. Adversários motivados podem foder com você com facilidade (leia a respeito de ataques de Timing, correlação e fingerprinting). Mesmo que não seja possível ver o conteúdo de uma mensagem pela deepweb, é possível ao menos saber que você a acessou. ISPs podem ver esse tipo de tráfego como suspeito. Você não é um hacker só porque instalou o TorBrowser, mas pode ser considerado um se expor o IP de um hidden service. ## Instalando e configurando o roteador I2P Segue agora a seção 2 do tutorial do I2P. Mas antes apenas queria falar um pouco do projeto I2P. Apesar do foco do tutorial não ser para tratar da sua história, gostaria ao menos de fazer uma breve introdução sobre ela. O projeto I2P (Invisible Internet Protocol) é uma rede P2P descentalizada, anônima e segura para estabelecer a comunicação entre os usuários e serviços. Na I2P é possível usar serviços como mensageiros IRC, XMPP, web services, e-mail e até mesmo torrents. A I2P nasceu de um fork da Freenet no ano de 2003, porém possui diferenças drásticas em relação a ela. Há similaridades entre a I2P e o Tor, porém vale destacar algumas de suas vantagens. Sendo elas: • Garlic routing ( https://geti2p.net/en/docs/how/garlic-routing ) • Modelo P2P • Todos os participantes da rede contribuem para ela • Fechado na rede - não é possível acessar a surface através da I2P • Otimizado para hidden services Apesar disso, vale lembrar que o projeto é pequeno, desenvolvido por menos voluntários se comparado ao Tor e possui menos movimentação e financiamento para o seu desenvolvimento. Além disso, o Tor é um projeto muito mais maduro e bem documentado, algo que atrai mais usuários e desenvolvedores e torna a tarefa de encontrar e corrigir bugs mais fácil de ser realizada. Esses são pontos importantes que devemos levar em conta ao escolher a tecnologia para as nossas necessidades. Nem sempre há tecnologias ruins, as vezes apenas as empregamos as ferramentas erradas na resolução de certos problemas. Referências: • https://geti2p.net/en/comparison/tor • https://geti2p.net/en/docs/how/garlic-routing • https://geti2p.net/en/about/intro • https://i2pd.readthedocs.io/en/latest/ ### 2. Instalando e configurando o roteador Antes da criação do I2PBrowserBundle ( https://github.com/PurpleI2P/i2pdbrowser/releases/tag/1.3.3 ) , a única forma de se conectar à I2P era pela configuração manual de proxy no navegador. Muita gente ou não sabe ou tem MUUUUUITA preguiça de fazer isso e ficam resistentes de entrar na I2P dada essa restrição. Como eu quero ser um bom tutor eu farei do jeito mais "difícil", pois tanto eu desejo que vocês aprendam as nuances do processo como eu sei que vocês são inteligentes o suficiente para fazer isso. ### 2.1 Instalação do router Atualmente nós temos duas implementações do I2P: Uma em Java e outra em C++ (i2pd). Usaremos nesse tutorial a versão em C++ dado o seu baixo uso de recursos e facilidade de instalação. O I2Pd está disponível para Windows, Linux, MacOS e Android e possui binários pré-compilados nas releases ( https://github.com/PurpleI2P/i2pd/releases/tag/2.50.2 ) do projeto no Github. Usuários de Linux podem instalá-lo através do respectivo gerenciador de pacotes da sua distribuição, porém algumas distros não oferecem o pacote diretamente nos reposítórios oficiais, necessitando do uso de PPAs (Ubuntu), COPR (Fedora/RHEL) e afins. Vocês podem conferir as instruções oficiais para cada sistema nessa página ( https://i2pd.readthedocs.io/en/latest/user-guide/install/ ). Apesar desse tutorial ser voltado a usuários de desktop, o I2Pd também está disponível na loja do F-droid. Infelizmente poucos navegadores em Android permitem a configuração de proxies, porém na seção de Serviços na I2P eu tratarei brevemente de como se conectar a servidores de XMPP usando o ConversationI2P. Para usuários de Windows, segue abaixo os binários para instalação. • Versão 32bits ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_win32_mingw.zip ) • Versão 64bits ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_win64_mingw.zip ) • Versão para Windows XP (pois é, kk) ( https://github.com/PurpleI2P/i2pd/releases/download/2.50.2/i2pd_2.50.2_winxp_mingw.zip ) A instalação é simples e direta. Após ela apenas abram o I2Pd para que o router inicie a operação de busca e conexão com os peers. Para usuários de Linux, vocês precisam ativar o serviços através do comando 'sudo systemctl start i2pd'. Se vocês desejam que o I2Pd inicie junto com o sistema usem o comando 'sudo systemctl enable --now i2pd'. Se tudo estiver funcionando corretamente, vocês serão capazes de abrir o webconsole do I2Pd no navegador através do endereço: 127.0.0.1:7070. https://image.nostr.build/ab205ae1071a2b705279e5ce2d6e912d8d11cc7d6dd0dc8a26b76724a27bd94b.jpg https://image.nostr.build/fa17e14600737ccfc92a415cec2fbfba226b950b2b97af7475927ae65abdbe11.jpg ### 2.2 Instalação e configuração do navegador Apesar de qualquer navegador ser capaz de usar a I2P não é recomendado que usem qualquer um, especialmente o navegador que você usam no seu dia-a-dia. Recomendo que usem um navegador próprio para usar na I2P ou isolem suas atividades em um perfil separado. Em navegadores baseado no Firefox isso é relativamente simples, bastando adicionar a opção '--profile' e o caminho do perfil que vocês desejam usar. Nesse tutorial eu vou mostrar como criar um perfil novo no Librewolf e configurar no lançador para iniciar o perfil e abrir em uma janela anônima. Essas instruções são análogas para todos os sistemas, excetuando aquelas configurações mais exóticas. ### 2.2.1 Escolhendo o navegador Como citado, usarei o Librewolf como exemplo. Vocês podem baixar o instalador direto do site ou usar o gerenciador de pacotes do seu sistema no caso de Linux. Como é uma tarefa trivial eu não vou detalhar esse processo, pois todas as instruções estão em detalhes no site do navegador ( https://librewolf.net/installation/ ) ### 2.2.2 Criando um perfil e configurando o lançador Abram o navegador e digitem 'about:profiles' na barra de endereço. Criem um novo perfil clicando em 'Create New Profile' https://image.nostr.build/fa17e14600737ccfc92a415cec2fbfba226b950b2b97af7475927ae65abdbe11.jpg Coloquem um nome no seu perfil e cliquem em Finalizar https://image.nostr.build/62059e375000940f11b27ae77b9ec011f9baadbb5a84afc910d41841ce73e82d.jpg Perfis novos recém criados são iniciados por padrão. Se você deseja usar outro perfil por padrão deve mudar isso na seção 'about:profiles' do navegador. Agora vamos configurar o lançador do LibreWolf para iniciar o perfil do i2p e em uma janela anônima. Usarei o XFCE como referência para essa tarefa, mas saibam que o processo é análogo em sistemas como Windows ou DEs como KDE. Se quiserem também podem lançar via terminal através do comando 'librewolf --profile caminho_do_perfil --private-window'. Cliquem com o botão direito no ícone do Librewolf e abram as propriedades do atalho. Na guia lançador, no campo Comando, adicionem no final a opção '--private-window' e a opção '--profile caminho_do_perfil'. O caminho do perfil é aquele mostrado na seção 'about:profiles' do Librewolf. https://image.nostr.build/a7d6515d7825cb3bdcb681ecf71a97318dccba81eea7cc87fc5377ecc06065ee.jpg 2.2.3 Configurando o proxy Com o lançador configurado, abra o navegador nesse perfil. Vamos configurar o proxy para se conectar ao I2P agora. Abra as configurações digitando 'about:preferences' na barra de endereço. Na seção 'Geral' abra as configurações de rede (Network Settings) https://image.nostr.build/f37157bebf15ada616914f403e756cf9fcee4c9aaaa353196c9cc754ca4d7bc5.jpg Configure o seu proxy como na figura abaixo. https://image.nostr.build/41ebd05255a8129d21011518d400689308d9c0320408967003bf296771e0b96f.jpg Fecha as configurações. Se o seu proxy foi configurado corretamente tente abrir algum desses eepsites. • http://identiguy.i2p • http://notbob.i2p • http://reg.i2p Se tudo ocorreu como conforme, a página será carregada. https://image.nostr.build/ce29ae44743f06cfed591f082208c9612c59b3429ab46d90db48131b3bc3e99d.jpg OBSERVAÇÃO: A busca pelos peers é um pouco demorada, levando de 2 a 5 minutos para que um número mínimo necessário de peers sejam encontrados para estabelecer uma conexão estável. Você pode ver a lista de inbound e outbound tunnels na seção Tunnels do WebConsole (localhost:7070) https://image.nostr.build/285a0d765eaf5f33409f975cd720d0efa68ecc40a9da20bfd9cde0cd1f59a7b6.jpg IMPORTANTE: Apesar do Librewolf possuir defaults seguros, eu recomendo que vocês instalem as seguintes extensões para aumentar ainda mais a sua proteção. • noScript • JShelter Lembrem-se que vocês precisam desativar o proxy para acessar a clearnet. Depois disso reativem-no nas configurações. Outro detalhe: Se vocês tentarem digitar um endereço .i2p na barra de endereços do navegador sem especificar o protocolo (http), ao invés do Librewolf ir ao endereço ele vai realizar uma pesquisa. Para corrigir esse problema, vocês precisam adicionar a seguinte configuração do tipo boolean em 'about:config' como mostrado na imagem. https://image.nostr.build/4518ab817b131f7efe542b2d919b926099dce29a7b59bdd3c788caf53dbd071e.jpg Reiniciem o navegador e testem. Se tudo deu certo vocês não precisam especificar o protocolo ao digitar um endereço .i2p, bastando apenas digitar o endereço simplificado. Por fim, terminamos essa parte do tutorial. Na próximo parte trataremos de como podemos nos conectar a serviços hospedados na I2P como XMPP ## [TUTORIAL] Conectando-se ao XMPP pela I2P Essa é a terceira parte da série de tutoriais. Agora vamos tratar de algumas operações na rede, sendo uma delas conectando-se a um servidor de XMPP na I2P. Não se esqueça de ligar o router e manter ele ligado por alguns minutos antes de iniciar essas operações. O router demora um pouco para encontrar os peers e estabelecer uma conexão estável. ### 3.1 Escolhendo o cliente XMPP Existem diversos clientes XMPP capazes de se conectar usando um proxy. Um dos melhores é o Gajim, um cliente escrito em Python com diversas funcionalidades como criptografia OMEMO e PGP, workspaces separados, extensibilidade via plugins e uma interface bonita e organizada. Assim como ocorreu com o router, o Gajim está disponível por padrão na maioria das distros Linux. Use o seu gerenciador de pacotes para instala-lo. Em Windows você pode baixar o Gajim através desse link ( https://gajim.org/download/ ) ### 3.2 Criando uma conta Vamos primeiro criar uma conta no servidor. No nosso exemplo usarei o servidor oficial do projeto i2pd, o xmpp.ilita.i2p. Há diversos outros servidores XMPP no diretório de links notbob.i2p caso queiram explorar mais. Para criar uma conta, siga os passos abaixo: Abra o Gajim. Na barra de tarefas vá em Contas -> Adicionar Conta. Na nova janela que aparecer, clique em Adicionar Conta https://image.nostr.build/01413e7c6d00c238420e3b0c769dd8d7f7d6522754d2135d3e98a22944f79a27.jpg https://image.nostr.build/9f015861f33990871d96f03d5ec78036a65e3ad9f8ff6a38da18c5b27d31f6d5.jpg Na janela de adicionar contas, clique diretamente em Inscrever-se. Não precisa colocar as suas credencias como mostra a imagem (falha minha, ksksk) https://nostrcheck.me/media/c8411a22946e97467e0ee197ef7a0205ba05f2c67bde092041481ccc2cbbc66d/81938c8d278ce0562c2240341e203f3b70f51ee2db06ceb453f8a178df37fa84.webp Digite o nome do servidor no campo abaixo. Não esqueça de marcar a opção 'Configurações Avançadas' antes de clicar em Inscrever-se https://image.nostr.build/5ee4305a6a23e5c064446b0ce7a4cbc7e790c1ba237bd2495d0237b86a4df07f.jpg Vamos adicionar um novo proxy para essa conta. Para isso clique no botão 'Gerenciar proxies', ao lado do campo Proxy nas Configurações Avançadas https://image.nostr.build/daceb5436def55401d3974ce48d85771e5ebcec4e3f90eb1001df4609112ec12.jpg Adicione um novo proxy clicando no sinal de '+' abaixo da lista de proxies. Preencha os campos de acordo com a imagem abaixo e em seguida feche a janela. https://image.nostr.build/140b34c4e46e9295c073311d483d206201d9339a75f613fe4e829c14f3257bfe.jpg https://image.nostr.build/d365a63d81a14d763bffceb50b30eb53d81959623f8fe812175358a41b1fba53.jpg No campo de Proxy, selecione o proxy I2P. Preencha o restante dos campos de acordo com a imagem abaixo. Em seguida clique em 'Inscrever-se'. https://image.nostr.build/d06c11d9c6d19728bf5a58af2dd3e14d8ca0021456da09792a345ac0bfc90ad0.jpg Nesse momento uma mensagem pode aparecer pedindo para abrir uma exceção para o certificado TLS. Isso acontece porque trata-se de um certificado autoassinado que não foi validado por uma autoridade oficial. Apenas abra a exceção e prossiga (não há imagem para isso porque eu já abri essa exceção no meu cliente). Uma nova janela vai aparecer solicitando-lhe para inserir as suas credenciais. Tome cuidado aqui, pois não é para inserir o nome completo com o domínio, apenas o seu nome de usuário (ex: descartavel). https://image.nostr.build/dde2a6736bd00080fbeeb8076754e226971a412710b370d5559f7f4d5414f8b3.jpg Se tudo der certo, uma nova janela vai aparecer confirmando a sua inscrição. Coloque um nome e uma cor para a sua conta e clique em Conectar para concluir o processo. https://image.nostr.build/74934d3f1f3f4232eacee8e78e707936227f816c50ac6b52da5c81ec17557e69.jpg Para finalizar, nos detalhes da sua conta, modifique as suas configurações de privacidade para diminuir o fingerprint. Na seção de 'Privacidade', desligue as seguintes opções: • Tempo ocioso • Hora de Sistema Local • Sistema Operacional • Reprodução de Mídia https://image.nostr.build/d2ed5852a104c770b50c7b053d518d8af0b6289ced6b3ad4187492208c7ca649.jpg ### 3.3 Procurando por salas de bate-papo públicas Após criar a sua nova conta, vamos descobrir alguns serviços que o servidor oferece. Para isso, vá para Contas -> Descobrir serviços https://image.nostr.build/54928d1dd0e48365858b24c72097a9fabf677794e13f329fc0568211eefbe559.jpg Na seção 'Bate-papo em Grupo', selecione Chatrooms e clique em 'Navegar'. Ao fazer isso uma lista de chatroom públicos presentes no servidor vai aparecer. Fique a vontade para explorar, porém saiba que alguns servidores são moderados e não te permitem mandar mensagens sem sua conta ser aprovada pelo moderador (familiar?). https://image.nostr.build/1936bef51d58a1f6cfdf8bf8d84bfa64adc2a09b9c0fb1623b93a327f0b8cdd8.jpg https://image.nostr.build/89e8013b1cea1df0f80f6833bd6771c33101f404b0099b2d7330a5e57607baff.jpg ### 3.4 Adicionando contatos Para adicionar contatos à sua lista, clique no símbolo de '+' ao lado do campo de pesquisa e selecione 'Add Contact'. https://image.nostr.build/d3cadea27591355f674fba93765c3815282d112b2e80a592bb77a442c13dd4f4.jpg Coloque o endereço completo da conta que você deseja adicionar. Usarei a minha conta oficial nesse exemplo. Você tem a opção de anexar uma mensagem qualquer antes de enviar o convite. Clique em 'Adicionar Contato' para prosseguir. https://image.nostr.build/ff95b7aec2377c58d4253c5b7b3aabf141a92dd5f3e97f6e1f01ecb32a215d38.jpg https://image.nostr.build/6562e680e28c321ebbd009b5ade513f8a279aea33bc16aa9fb251f3507eb04af.jpg Se tudo ocorrer normalmente, o novo contato vai aparecer na sua lista. Dê dois-cliques na conta para abrir o chat. Não se esqueça de ativar a criptografia OMEMO antes de enviar qualquer mensagem. Agora você está pronto para conversar de forma segura :) https://image.nostr.build/ef7f783a311ad0f68a5408137f75dc2bc6c38f6e9656dc0d68d3267f5012f658.jpg E com isso terminamos a terceira parte da série de tutoriais. ## [TUTORIAL] Criando e conectando-se a um servidor XMPP na I2P e clearnet. Como configurar o seu próprio servidor XMPP. https://youtube.com/watch?v=Ot_EmQ8xdJwy Criando contas e conectando clientes Pidgin http://i2pd.readthedocs.io/en/latest/tutorials/xmpp/#creating-accounts-and-connecting-clients BONUS: Conectando-se facilmente à I2P. https://youtube.com/watch?v=wGIh5tQcw68 @ fd208ee8:0fd927c1
2024-10-29 08:52:42## Yesterday was also a day I'm still quite bullish about using Nostr to publish, and generally for OtherStuff, but I was feeling a bit pessimistic about the microblogging (kind 01) feeds on Nostr, yesterday. And, rightly so. Mine has been grinding slowly to a halt, and not for lack of effort, on my part. I regularly hear reports, from other npubs, that they sense the same phenomenon. Most of the people I have whitelisted on the wss://theforest.nostr1.com relay (currently 302, in number) are beginning to give up on Kind 01 clients, except for occasionally making an announcement, and are increasingly moving their chatting off-Nostr. (I'm still privy to those conversations, but most of you no longer are.) So, my feed has been getting quieter and quieter. Even adding new people doesn't help much, as they don't tend to stick around, for long, so it's a Sisyphean task.  Some others are still bothering to show up, regularly, but they increasingly see it as a chore, or something they do to "keep up appearances". Add me to this group of wearied, diligent noters, holding down the microblogging feeds, with our exhausting attempt at #KeepingNostrWeird, while the influencers surround the gates and the Kind 01 feeds dissolve into nothing but warmed-over Bitcoin memes, GM notes, notifications from the OtherStuff, and Things Copied from X.  The problem of barren, intellectually-emptying Kind 01 feeds is further exacerbated by the fact that new entrants to the Nostrverse find it increasingly easy to "find good follows", but they're all only finding the same follows: whoever is on the trending list. ## The See-Nothings I keep complaining about this, but the responses I get are generally unhelpful. They are: * mockery -- Oh, Miss Hoity-Toity wants more attention! * insults -- Nobody is talking to you because you are boring and stupid, and nobody likes you. * clueless -- You should try replying to other people, then they might reply to you. * or they tell me to just stop looking at the list, if it upsets me.  What people are missing, by telling me to just not look at the trending lists, is that the lists are a statistic of what real humans are looking at, on Nostr. The bizarrely-high concentration of npubs, on the list, so that their entries show up multiple times, suggests that what people are primarily looking at... is the trending list. 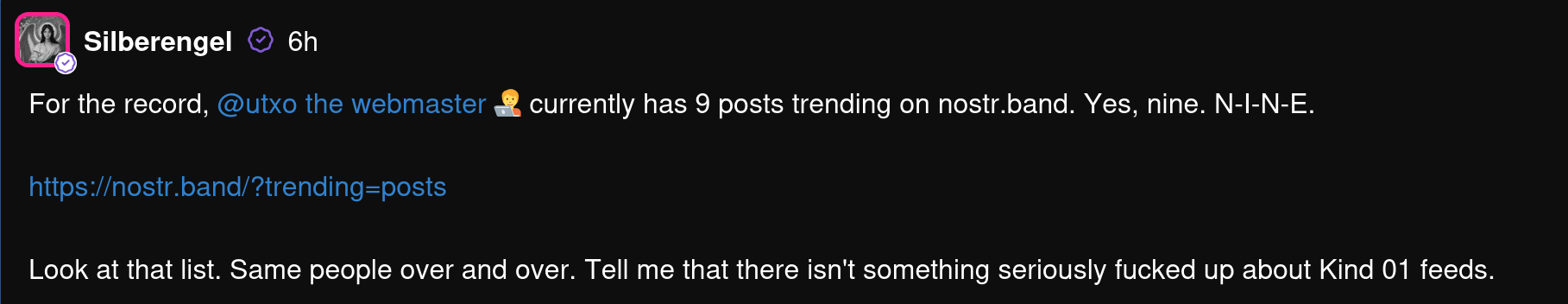 Either directly, because they use a client that has that built in, or indirectly, as they have been onboarded with the lists or told to "just follow the people I follow", which leads to a steadily-rising concentration of follows. This concentrating effect is accelerating. The newly-popular WoT (web of trust) relays further exacerbate this effect, as they put a premium on the npubs that have the highest WoT score, which -- surprise, surprise! -- are the same people as on the trending list. And this is why everyone on the trending list insists Nostr is a fun, happening place, full of human interaction. A place where replying reverently to Jack and posting GM religiously will make you a sought-after conversant. It is that place. For them. In fact, they've reached that glorious state of #PeakSocialMedia, where they have become famous for being famous, and no longer have to even pretend to be trying to appeal to anyone with their content. They can post literal garbage, and their ~~fans~~ ~~groupies~~ ~~sycophants~~ commentariat will cheer them on, and flood their replies with ardent encouragement. Less because those other npubs actually cared about what they posted, than because they are hoping to pick up new followers in those threads, since they know that everyone is looking at those threads, because those threads are trending. It's a pyramid scheme of following. 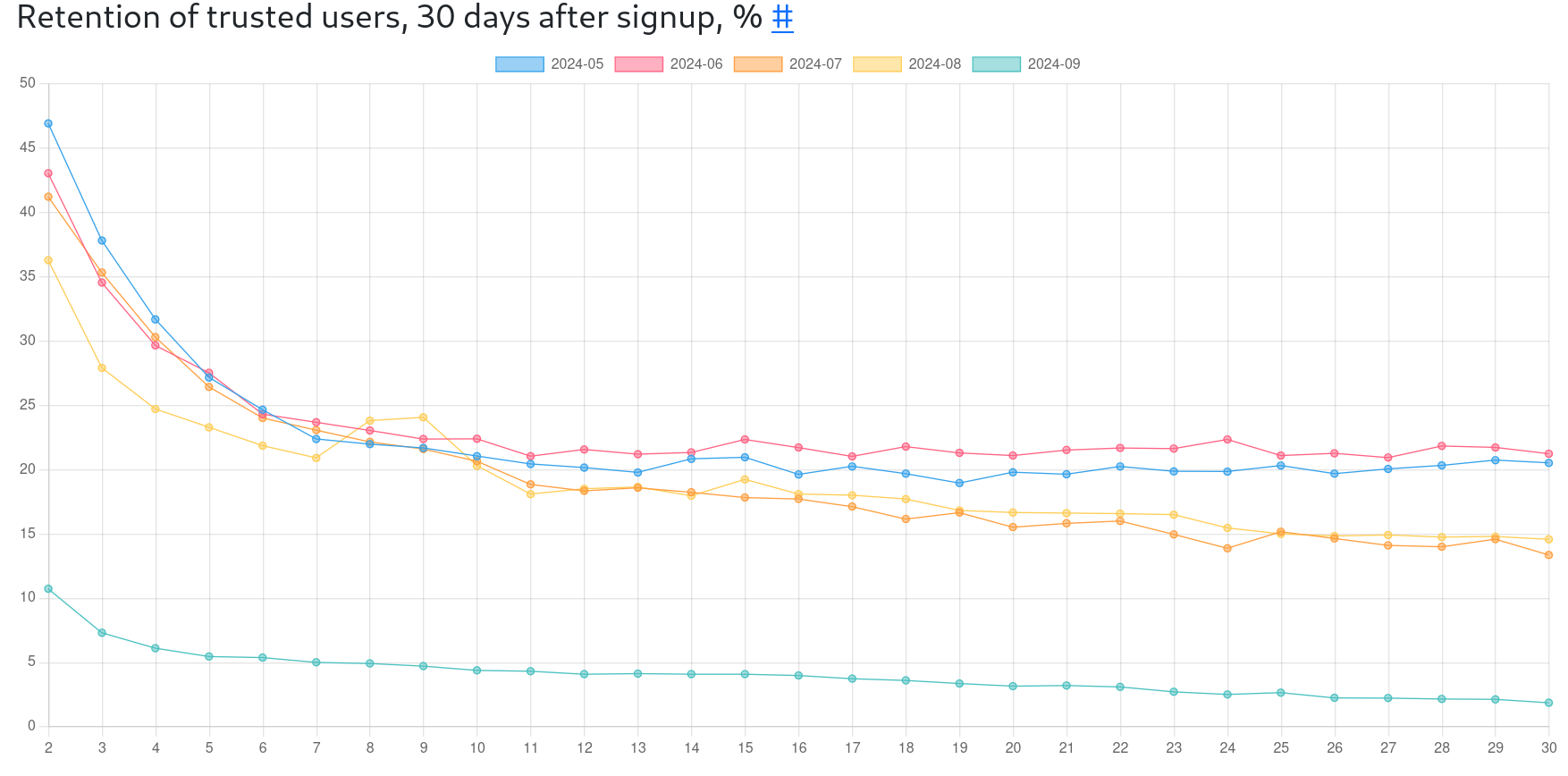 For the rest of us... the vast majority of us... that blue line at the bottom is mostly how it feels. ## The trend is to trending. What we no longer have, is people looking directly at relay feeds, to find new people, or even their own follow list feeds, to see npubs they've already subscribed to. Even when people follow me, they usually don't respond until I'm trending, which suggests that they're also seeing me on the trending list because that is what they're primarily looking at. This is why, as soon as you get on the trending list, your replies explode. And your replies will be concentrated in a hardcore few, otherwise. Those few are the reason I keep coming back, but as they're also often chatting with me off-Nostr, I am facing the question of: _Why bother with Nostr microblogging?_ This is the question I am struggling with. If kind 01 isn't for plebs chatting, anymore, (and it increasingly isn't) then it's mostly a sort of bulletin board, where we post notifications of items we've added in OtherStuff clients, or make announcements of meetups, software releases, or conferences. This, however, is compounding the dullness of the feeds and turning it into a sort of "info flyer", except for a lucky few. But, perhaps, I am simply a #NostrBoomer, who is failing to move with the times and get with the program.  I'm slowly reaching the conclusion that Kind 01 in an open, centralized market of notes, will always coalesce around a small subset of #NostrElite and turn into a largely passive form of entertainment, or a frustratingly lonely place, for everyone else. There can only be so many people talking, at once, in a public square. The only movement I currently see, that might end the slow slide of Kind 01 into irrelevance and tedium, is to create lots of smaller, public squares, through single-relay communities. This has been such a long time, in coming, and has been resisted by client devs so ferociously, that I worry that it's merely an attempt to close the barn door after the npubs have escaped. I sincerely hope to be proven wrong, though. Perhaps the relay devs, who have valiantly taken up the fight, will #SaveKind01. We shall see.
@ fd208ee8:0fd927c1
2024-10-29 08:52:42## Yesterday was also a day I'm still quite bullish about using Nostr to publish, and generally for OtherStuff, but I was feeling a bit pessimistic about the microblogging (kind 01) feeds on Nostr, yesterday. And, rightly so. Mine has been grinding slowly to a halt, and not for lack of effort, on my part. I regularly hear reports, from other npubs, that they sense the same phenomenon. Most of the people I have whitelisted on the wss://theforest.nostr1.com relay (currently 302, in number) are beginning to give up on Kind 01 clients, except for occasionally making an announcement, and are increasingly moving their chatting off-Nostr. (I'm still privy to those conversations, but most of you no longer are.) So, my feed has been getting quieter and quieter. Even adding new people doesn't help much, as they don't tend to stick around, for long, so it's a Sisyphean task.  Some others are still bothering to show up, regularly, but they increasingly see it as a chore, or something they do to "keep up appearances". Add me to this group of wearied, diligent noters, holding down the microblogging feeds, with our exhausting attempt at #KeepingNostrWeird, while the influencers surround the gates and the Kind 01 feeds dissolve into nothing but warmed-over Bitcoin memes, GM notes, notifications from the OtherStuff, and Things Copied from X.  The problem of barren, intellectually-emptying Kind 01 feeds is further exacerbated by the fact that new entrants to the Nostrverse find it increasingly easy to "find good follows", but they're all only finding the same follows: whoever is on the trending list. ## The See-Nothings I keep complaining about this, but the responses I get are generally unhelpful. They are: * mockery -- Oh, Miss Hoity-Toity wants more attention! * insults -- Nobody is talking to you because you are boring and stupid, and nobody likes you. * clueless -- You should try replying to other people, then they might reply to you. * or they tell me to just stop looking at the list, if it upsets me.  What people are missing, by telling me to just not look at the trending lists, is that the lists are a statistic of what real humans are looking at, on Nostr. The bizarrely-high concentration of npubs, on the list, so that their entries show up multiple times, suggests that what people are primarily looking at... is the trending list.  Either directly, because they use a client that has that built in, or indirectly, as they have been onboarded with the lists or told to "just follow the people I follow", which leads to a steadily-rising concentration of follows. This concentrating effect is accelerating. The newly-popular WoT (web of trust) relays further exacerbate this effect, as they put a premium on the npubs that have the highest WoT score, which -- surprise, surprise! -- are the same people as on the trending list. And this is why everyone on the trending list insists Nostr is a fun, happening place, full of human interaction. A place where replying reverently to Jack and posting GM religiously will make you a sought-after conversant. It is that place. For them. In fact, they've reached that glorious state of #PeakSocialMedia, where they have become famous for being famous, and no longer have to even pretend to be trying to appeal to anyone with their content. They can post literal garbage, and their ~~fans~~ ~~groupies~~ ~~sycophants~~ commentariat will cheer them on, and flood their replies with ardent encouragement. Less because those other npubs actually cared about what they posted, than because they are hoping to pick up new followers in those threads, since they know that everyone is looking at those threads, because those threads are trending. It's a pyramid scheme of following. 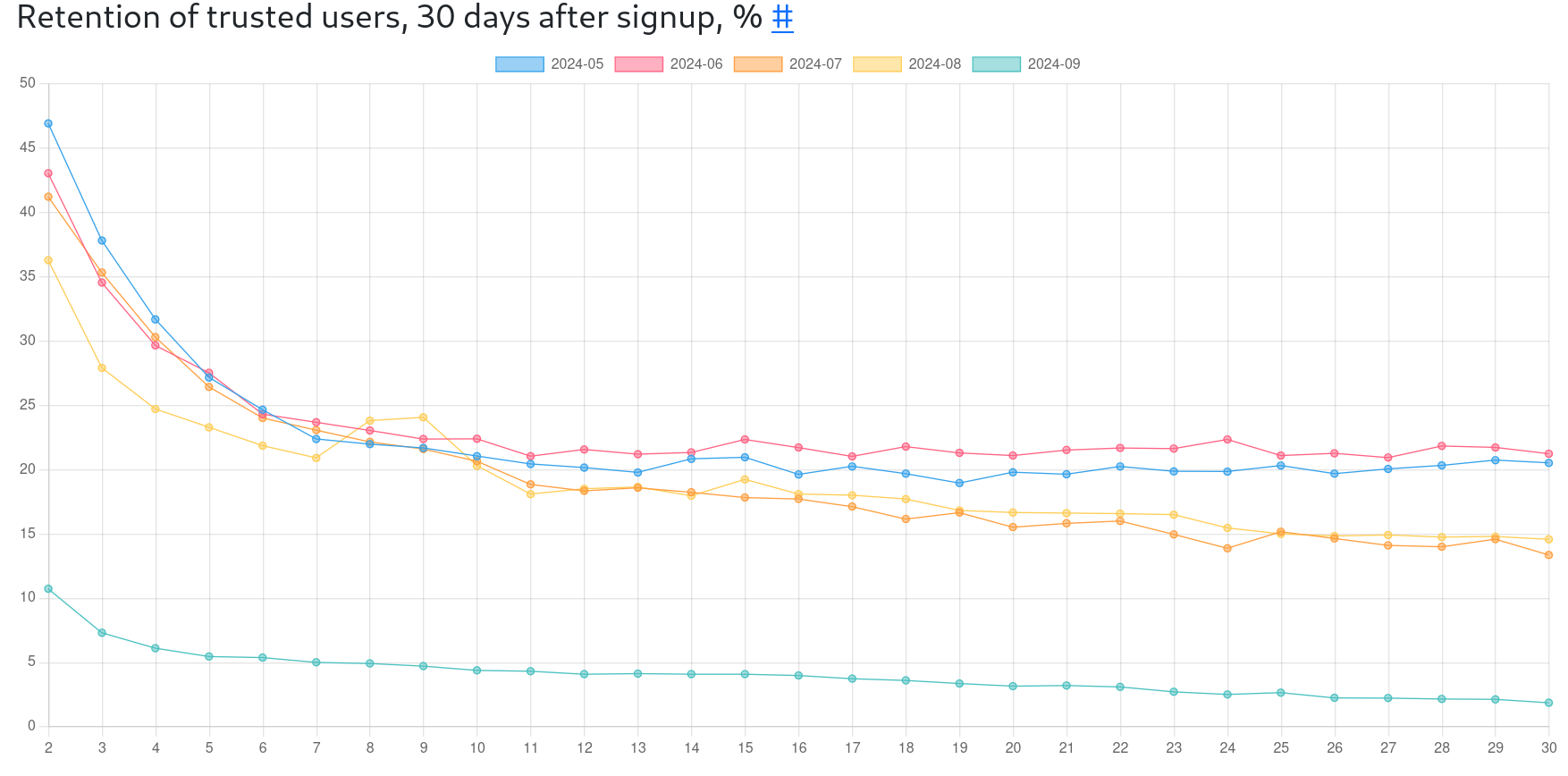 For the rest of us... the vast majority of us... that blue line at the bottom is mostly how it feels. ## The trend is to trending. What we no longer have, is people looking directly at relay feeds, to find new people, or even their own follow list feeds, to see npubs they've already subscribed to. Even when people follow me, they usually don't respond until I'm trending, which suggests that they're also seeing me on the trending list because that is what they're primarily looking at. This is why, as soon as you get on the trending list, your replies explode. And your replies will be concentrated in a hardcore few, otherwise. Those few are the reason I keep coming back, but as they're also often chatting with me off-Nostr, I am facing the question of: _Why bother with Nostr microblogging?_ This is the question I am struggling with. If kind 01 isn't for plebs chatting, anymore, (and it increasingly isn't) then it's mostly a sort of bulletin board, where we post notifications of items we've added in OtherStuff clients, or make announcements of meetups, software releases, or conferences. This, however, is compounding the dullness of the feeds and turning it into a sort of "info flyer", except for a lucky few. But, perhaps, I am simply a #NostrBoomer, who is failing to move with the times and get with the program.  I'm slowly reaching the conclusion that Kind 01 in an open, centralized market of notes, will always coalesce around a small subset of #NostrElite and turn into a largely passive form of entertainment, or a frustratingly lonely place, for everyone else. There can only be so many people talking, at once, in a public square. The only movement I currently see, that might end the slow slide of Kind 01 into irrelevance and tedium, is to create lots of smaller, public squares, through single-relay communities. This has been such a long time, in coming, and has been resisted by client devs so ferociously, that I worry that it's merely an attempt to close the barn door after the npubs have escaped. I sincerely hope to be proven wrong, though. Perhaps the relay devs, who have valiantly taken up the fight, will #SaveKind01. We shall see. @ a39d19ec:3d88f61e
2024-10-28 18:44:55##### What do you even print with it besides decorative objects? This kind of question still is a common one when talking about 3d printing. With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot. Let me start the series with a nice little print consisting of two parts. ## Laptop riser There are many designs of laptop risers available online. But I like that the parts are small and interlocking, so that the are always together when not in use. The riser fits all laptops in our house. Particularly when working in Fusion360 my laptop needs lots of fresh air. I use the raiser regularly about 3 times a week. Sadly I don't know where I downloaded it from, so I cannot provide a link to it. 
@ a39d19ec:3d88f61e
2024-10-28 18:44:55##### What do you even print with it besides decorative objects? This kind of question still is a common one when talking about 3d printing. With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot. Let me start the series with a nice little print consisting of two parts. ## Laptop riser There are many designs of laptop risers available online. But I like that the parts are small and interlocking, so that the are always together when not in use. The riser fits all laptops in our house. Particularly when working in Fusion360 my laptop needs lots of fresh air. I use the raiser regularly about 3 times a week. Sadly I don't know where I downloaded it from, so I cannot provide a link to it.  @ 8d34bd24:414be32b
2024-10-27 22:30:18NOTE: *This article has some details that are specific to America, but the overall principles are applicable to all, and I believe it will be useful for all Christians.* When it comes to things like voting, Christians tend to err to one of two extremes and seem to find difficulty finding the right balance as defined by God. Some Christians refuse to vote or get involved with politics at all. They don’t want to dirty themselves with politics. They know that their true home is heaven, so they don’t seem to care much for the nations they live in. On the other hand, some Christians are so focused on politics fixing everything and creating heaven on earth that they can become idolatrous lifting up politicians as a kind of savior. In this article, I’m going to address both extremes, using the Bible, and hopefully help you find a Biblical balance. ## Seek the Welfare of the City Where I Have Sent You As Christians we are just passing through our time on earth. Our true, eternal home, our true citizenship, is in heaven. That doesn’t mean that we shouldn’t care what happens on earth. We shouldn’t be like the old saying, “some Christians are so heavenly minded that they aren’t any earthly good.” I think Christians should organize our time here on earth kind of like the Israelites were commanded to live during their 70 year exile in Babylon and Persia. > Now these are the words of the letter which Jeremiah the prophet sent from Jerusalem to the rest of the elders of the exile, the priests, the prophets and all the people whom Nebuchadnezzar had taken into exile from Jerusalem to Babylon. (Jeremiah 29:1) What did God say to the Israelites about how they should live their life in Babylon? > “Thus says the Lord of hosts, the God of Israel, to all the exiles whom I have sent into exile from Jerusalem to Babylon, ‘Build houses and live in them; and plant gardens and eat their produce. Take wives and become the fathers of sons and daughters, and take wives for your sons and give your daughters to husbands, that they may bear sons and daughters; and multiply there and do not decrease. **Seek the welfare of the city where I have sent you into exile, and pray to the Lord on its behalf; for in its welfare you will have welfare**.’ (Jeremiah 29:4-7) {emphasis mine} Could we likewise say the same to Christians during their time on earth? “Build houses and live in them; and plant gardens and eat their produce. Take wives and become the fathers of sons and daughters, and take wives for your sons and give your daughters to husbands, that they may bear sons and daughters; and multiply there and do not decrease. Seek the welfare of the city, state, or nation where I have sent you to live for a short while, and pray to the Lord on its behalf; for in its welfare you will have welfare.” God expects us to live fruitful lives, to marry, to have many children (multiply), and to raise them up to do the same. He also wants us to seek the welfare of the city, state, and nation where God has put us. In a city, state, or nation with democratic elections, the best way to seek its welfare is to vote for honest candidates who support godly principles. We rightly understand that in our ungodly world there are no perfect candidates. It can even be hard to find mostly honest and mostly godly candidates, but we should seek to elect the best that is available. Why are we told to do this? We are told that “*for in its welfare you will have welfare*.” When we fail to vote, to teach our kids or support good schools, to live productive lives, and to generally live Godly lives, we WILL see the decline of our cities, states, and nations. We will pay the price. We are seeing exactly that decline because Christians have pulled out (and were pushed out) of the positions that influence the culture. We don’t have enough godly teachers, journalists, professors, advisors, economists, and politicians. We have given up the culture to those who oppose God, His people, and His commands. We are paying the price for withdrawing into the safety of our churches and leaving the world to the wolves. ## Political Religion Of course we also have an opposite extreme. We have some Christians that are too focused on politics and power. They spend all of their time and energy on political endeavors and very little, to none, on sharing the Gospel and being a godly example. Many act like they think a political candidate is going to save them from the culture, the media, the bureaucracy, or the government. They forget that there is only one Savior — the Lord Jesus Christ. They forget that God said things will get worse before they get better. They make idols out of politicians and religions out of political parties. > No servant can serve two masters; for either he will hate the one and love the other, or else he will be devoted to one and despise the other. You cannot serve God and wealth.” (Luke 16:13) Although this verse is specifically talking about being obsessed with wealth, it is applicable to anything that takes our focus, attention, and especially our worship away from God. When a person spends all of their time serving one candidate or party and little to no time serving God, they have chosen to serve another god and are guilty, even if inadvertently and unintentionally. > You shall have no other gods before Me. > > You shall not make for yourself an idol, or any likeness of what is in heaven above or on the earth beneath or in the water under the earth. You shall not worship them or serve them; for I, the Lord your God, am a jealous God, visiting the iniquity of the fathers on the children, on the third and the fourth generations of those who hate Me, but showing lovingkindness to thousands, to those who love Me and keep My commandments. (Exodus 20:3-6) When we look to a politician to save us from anything, we are making him/her a god before us. When we give our all to a political party, we are taking our heart away from God and giving it to an alternate religion. We may not think that we make idols in our modern world. It is true that we don’t usually carve them out of wood or mold them out of gold, but we have just as many idols as the Israelites did. They just look different. I hope you will seriously consider this next point because it may be very unpopular with many of my readers. There are lots of Christians that will throw as big, if not a bigger, fit at the desecration of the American flag than over the Bible. Nobody seems to fight to retain the pledge of allegiance more than a majority of Christians. I’d argue that the American flag has become a modern day idol and the “Pledge of Allegiance” has become a religious mantra repeated to the god of government. Look at the words of the pledge: *I pledge allegiance to the Flag of the United States of America,\ and to the Republic for which it stands,\ one Nation under God,\ indivisible, with liberty and justice for all.* I think the inclusion of the phrase “one Nation under God” makes Christians feel OK about this pledge originally invented by a socialist whose brother sold American flags. The important part, which is why I can’t say the pledge anymore, are the words, “I pledge allegiance to the Flag of the United States of America, and to the Republic for which it stands.” I really appreciate the principles America was founded upon, but as a Christian, I can only pledge allegiance to God. My allegiance isn’t to a flag (an idol) or the government (a god). I refuse to go through a religious ritual that includes particular stances, reciting special words, and showing undue respect. We cannot “*serve two masters*.” As Christians our master should be Christ alone. Anything that becomes more important than, or even equal to, the importance of God in our lives is idolatry. We need to get our priorities right. ## In the World, but Not of the World As we live our lives here on earth, we need to remember our God ordained purpose and our true allegiance to God. We need to remember our citizenship[1](https://trustjesus.substack.com/p/should-christians-vote#footnote-1-150236181) and family are in heaven, not here on earth. We want to have a positive influence on our culture, including working in influential positions and voting, but we should be most focused on personal evangelism and sharing the truth of the Bible. The best way to make a difference in our culture is to change hearts and minds through the Gospel of Jesus Christ. > But now I come to You; and these things I speak in the world so that they may have My joy made full in themselves. **I have given them Your word; and the world has hated them, because they are not of the world**, even as I am not of the world. I do not ask You to take them out of the world, but to keep them from the evil one. **They are not of the world, even as I am not of the world**. Sanctify them in the truth; **Your word is truth**. (John 17:13-17) {emphasis mine} Although we want to be a light in the world, we have been warned that doing so will make us not fit in. It will cause many non-Christians (and maybe a few Christians whose priorities are not right) to hate us. No matter the consequences, we need to stand on the truth of the Word of God. Too often, because we are living with those who are of this world, we start to look and act a lot like those of the world instead of looking and acting like our Savior. > **Do not love the world nor the things in the world**. If anyone loves the world, the love of the Father is not in him. For all that is in the world, the lust of the flesh and the lust of the eyes and the boastful pride of life, is not from the Father, but is from the world. **The world is passing away**, and also its lusts; but **the one who does the will of God lives forever**. (1 John 2:15-17) {emphasis mine} The fact that we should not love the things of the world or take on the character of things of the world is true in every part of our lives, but since we are talking here about politics, let us discuss the way many Christians talk politics. Many Christians talk about politics in the same manner as non-Christians — cursing, name calling, insulting, and doing whatever it takes to win, no matter whether it is moral or not. I know the “other side” cheats, lies, name-calls, etc., but we should not stoop to their level. Nobody ever won another to their point of view by cursing or name calling. There are ways to point our their errors, and even how horrific some of the things pushed are, without going so low. Jesus didn’t hold back from speaking the truth. He didn’t hesitate to point out error, but was never crude about it. We should be the same. We should shine a light in such a way that those around us see such a difference that they say something similar to what was said about the apostles: > Now as they observed the confidence of Peter and John and understood that they were uneducated and untrained men, they were amazed, and began to recognize them as having been with Jesus. (Acts 4:13) There should be something about our words, actions, and demeanor that amazes our opponents causing them to recognize us “*as having been with Jesus*.” I hope this post has been helpful, truthful, and not too offensive. In so many areas it is hard to find that perfect balance and to not allow ourselves to be pulled to either extreme to the detriment of our witness and our relationship to God. > Give no offense either to Jews or to Greeks or to the church of God; just as I also please all men in all things, not seeking my own profit but the profit of the many, **so that they may be saved**. (1 Corinthians 10:32-33) {emphasis mine} Trust Jesus.\ \ your sister in Christ, Christy
@ 8d34bd24:414be32b
2024-10-27 22:30:18NOTE: *This article has some details that are specific to America, but the overall principles are applicable to all, and I believe it will be useful for all Christians.* When it comes to things like voting, Christians tend to err to one of two extremes and seem to find difficulty finding the right balance as defined by God. Some Christians refuse to vote or get involved with politics at all. They don’t want to dirty themselves with politics. They know that their true home is heaven, so they don’t seem to care much for the nations they live in. On the other hand, some Christians are so focused on politics fixing everything and creating heaven on earth that they can become idolatrous lifting up politicians as a kind of savior. In this article, I’m going to address both extremes, using the Bible, and hopefully help you find a Biblical balance. ## Seek the Welfare of the City Where I Have Sent You As Christians we are just passing through our time on earth. Our true, eternal home, our true citizenship, is in heaven. That doesn’t mean that we shouldn’t care what happens on earth. We shouldn’t be like the old saying, “some Christians are so heavenly minded that they aren’t any earthly good.” I think Christians should organize our time here on earth kind of like the Israelites were commanded to live during their 70 year exile in Babylon and Persia. > Now these are the words of the letter which Jeremiah the prophet sent from Jerusalem to the rest of the elders of the exile, the priests, the prophets and all the people whom Nebuchadnezzar had taken into exile from Jerusalem to Babylon. (Jeremiah 29:1) What did God say to the Israelites about how they should live their life in Babylon? > “Thus says the Lord of hosts, the God of Israel, to all the exiles whom I have sent into exile from Jerusalem to Babylon, ‘Build houses and live in them; and plant gardens and eat their produce. Take wives and become the fathers of sons and daughters, and take wives for your sons and give your daughters to husbands, that they may bear sons and daughters; and multiply there and do not decrease. **Seek the welfare of the city where I have sent you into exile, and pray to the Lord on its behalf; for in its welfare you will have welfare**.’ (Jeremiah 29:4-7) {emphasis mine} Could we likewise say the same to Christians during their time on earth? “Build houses and live in them; and plant gardens and eat their produce. Take wives and become the fathers of sons and daughters, and take wives for your sons and give your daughters to husbands, that they may bear sons and daughters; and multiply there and do not decrease. Seek the welfare of the city, state, or nation where I have sent you to live for a short while, and pray to the Lord on its behalf; for in its welfare you will have welfare.” God expects us to live fruitful lives, to marry, to have many children (multiply), and to raise them up to do the same. He also wants us to seek the welfare of the city, state, and nation where God has put us. In a city, state, or nation with democratic elections, the best way to seek its welfare is to vote for honest candidates who support godly principles. We rightly understand that in our ungodly world there are no perfect candidates. It can even be hard to find mostly honest and mostly godly candidates, but we should seek to elect the best that is available. Why are we told to do this? We are told that “*for in its welfare you will have welfare*.” When we fail to vote, to teach our kids or support good schools, to live productive lives, and to generally live Godly lives, we WILL see the decline of our cities, states, and nations. We will pay the price. We are seeing exactly that decline because Christians have pulled out (and were pushed out) of the positions that influence the culture. We don’t have enough godly teachers, journalists, professors, advisors, economists, and politicians. We have given up the culture to those who oppose God, His people, and His commands. We are paying the price for withdrawing into the safety of our churches and leaving the world to the wolves. ## Political Religion Of course we also have an opposite extreme. We have some Christians that are too focused on politics and power. They spend all of their time and energy on political endeavors and very little, to none, on sharing the Gospel and being a godly example. Many act like they think a political candidate is going to save them from the culture, the media, the bureaucracy, or the government. They forget that there is only one Savior — the Lord Jesus Christ. They forget that God said things will get worse before they get better. They make idols out of politicians and religions out of political parties. > No servant can serve two masters; for either he will hate the one and love the other, or else he will be devoted to one and despise the other. You cannot serve God and wealth.” (Luke 16:13) Although this verse is specifically talking about being obsessed with wealth, it is applicable to anything that takes our focus, attention, and especially our worship away from God. When a person spends all of their time serving one candidate or party and little to no time serving God, they have chosen to serve another god and are guilty, even if inadvertently and unintentionally. > You shall have no other gods before Me. > > You shall not make for yourself an idol, or any likeness of what is in heaven above or on the earth beneath or in the water under the earth. You shall not worship them or serve them; for I, the Lord your God, am a jealous God, visiting the iniquity of the fathers on the children, on the third and the fourth generations of those who hate Me, but showing lovingkindness to thousands, to those who love Me and keep My commandments. (Exodus 20:3-6) When we look to a politician to save us from anything, we are making him/her a god before us. When we give our all to a political party, we are taking our heart away from God and giving it to an alternate religion. We may not think that we make idols in our modern world. It is true that we don’t usually carve them out of wood or mold them out of gold, but we have just as many idols as the Israelites did. They just look different. I hope you will seriously consider this next point because it may be very unpopular with many of my readers. There are lots of Christians that will throw as big, if not a bigger, fit at the desecration of the American flag than over the Bible. Nobody seems to fight to retain the pledge of allegiance more than a majority of Christians. I’d argue that the American flag has become a modern day idol and the “Pledge of Allegiance” has become a religious mantra repeated to the god of government. Look at the words of the pledge: *I pledge allegiance to the Flag of the United States of America,\ and to the Republic for which it stands,\ one Nation under God,\ indivisible, with liberty and justice for all.* I think the inclusion of the phrase “one Nation under God” makes Christians feel OK about this pledge originally invented by a socialist whose brother sold American flags. The important part, which is why I can’t say the pledge anymore, are the words, “I pledge allegiance to the Flag of the United States of America, and to the Republic for which it stands.” I really appreciate the principles America was founded upon, but as a Christian, I can only pledge allegiance to God. My allegiance isn’t to a flag (an idol) or the government (a god). I refuse to go through a religious ritual that includes particular stances, reciting special words, and showing undue respect. We cannot “*serve two masters*.” As Christians our master should be Christ alone. Anything that becomes more important than, or even equal to, the importance of God in our lives is idolatry. We need to get our priorities right. ## In the World, but Not of the World As we live our lives here on earth, we need to remember our God ordained purpose and our true allegiance to God. We need to remember our citizenship[1](https://trustjesus.substack.com/p/should-christians-vote#footnote-1-150236181) and family are in heaven, not here on earth. We want to have a positive influence on our culture, including working in influential positions and voting, but we should be most focused on personal evangelism and sharing the truth of the Bible. The best way to make a difference in our culture is to change hearts and minds through the Gospel of Jesus Christ. > But now I come to You; and these things I speak in the world so that they may have My joy made full in themselves. **I have given them Your word; and the world has hated them, because they are not of the world**, even as I am not of the world. I do not ask You to take them out of the world, but to keep them from the evil one. **They are not of the world, even as I am not of the world**. Sanctify them in the truth; **Your word is truth**. (John 17:13-17) {emphasis mine} Although we want to be a light in the world, we have been warned that doing so will make us not fit in. It will cause many non-Christians (and maybe a few Christians whose priorities are not right) to hate us. No matter the consequences, we need to stand on the truth of the Word of God. Too often, because we are living with those who are of this world, we start to look and act a lot like those of the world instead of looking and acting like our Savior. > **Do not love the world nor the things in the world**. If anyone loves the world, the love of the Father is not in him. For all that is in the world, the lust of the flesh and the lust of the eyes and the boastful pride of life, is not from the Father, but is from the world. **The world is passing away**, and also its lusts; but **the one who does the will of God lives forever**. (1 John 2:15-17) {emphasis mine} The fact that we should not love the things of the world or take on the character of things of the world is true in every part of our lives, but since we are talking here about politics, let us discuss the way many Christians talk politics. Many Christians talk about politics in the same manner as non-Christians — cursing, name calling, insulting, and doing whatever it takes to win, no matter whether it is moral or not. I know the “other side” cheats, lies, name-calls, etc., but we should not stoop to their level. Nobody ever won another to their point of view by cursing or name calling. There are ways to point our their errors, and even how horrific some of the things pushed are, without going so low. Jesus didn’t hold back from speaking the truth. He didn’t hesitate to point out error, but was never crude about it. We should be the same. We should shine a light in such a way that those around us see such a difference that they say something similar to what was said about the apostles: > Now as they observed the confidence of Peter and John and understood that they were uneducated and untrained men, they were amazed, and began to recognize them as having been with Jesus. (Acts 4:13) There should be something about our words, actions, and demeanor that amazes our opponents causing them to recognize us “*as having been with Jesus*.” I hope this post has been helpful, truthful, and not too offensive. In so many areas it is hard to find that perfect balance and to not allow ourselves to be pulled to either extreme to the detriment of our witness and our relationship to God. > Give no offense either to Jews or to Greeks or to the church of God; just as I also please all men in all things, not seeking my own profit but the profit of the many, **so that they may be saved**. (1 Corinthians 10:32-33) {emphasis mine} Trust Jesus.\ \ your sister in Christ, Christy @ a39d19ec:3d88f61e
2024-10-27 10:26:03**October's daily driver is the ana-digi Casio ABX-53 Twincept with module 1326. It features are world time, stopwatch, alarm and a databank for contacts.**  ## Design I have the gold/silver colored variant with a metal band. The watch has an analog clock and a floating display with the features listed above. Best thing is the "slider" mode that switches digital functions permanently. ## Storytime My log tells me that i bought the watch 6 years ago on a local flea market for close to nothing. It was in a bad condition and needed a new battery and some love. Sure enough it works fine since then. Most badass feature is that the analog hands are moved electronically not mechanically. Fun fact is that even my wife likes the floating display. First time she saw it I heard her say "Das ist echt cool", meaning "thats really cool".
@ a39d19ec:3d88f61e
2024-10-27 10:26:03**October's daily driver is the ana-digi Casio ABX-53 Twincept with module 1326. It features are world time, stopwatch, alarm and a databank for contacts.**  ## Design I have the gold/silver colored variant with a metal band. The watch has an analog clock and a floating display with the features listed above. Best thing is the "slider" mode that switches digital functions permanently. ## Storytime My log tells me that i bought the watch 6 years ago on a local flea market for close to nothing. It was in a bad condition and needed a new battery and some love. Sure enough it works fine since then. Most badass feature is that the analog hands are moved electronically not mechanically. Fun fact is that even my wife likes the floating display. First time she saw it I heard her say "Das ist echt cool", meaning "thats really cool". @ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also [addressing her Bill No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation. https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0 [(PT-BR version here)](https://www.eddieoz.com/drex-e-o-fim-do-dinheiro-fisico-no-brasil/) ## **What is a CBDC?** Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency. A prominent feature of CBDCs is their **programmability**. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area. In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously. ## **Practical Example: The Case of DREX During the Pandemic** To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, [the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence](https://youtu.be/cjUz2VEk4co?feature=shared&t=484&ref=eddieoz.com), limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice. To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government. ## **How Does China's Social Credit System Work?** Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, [including financial behavior, criminal record, social interactions, and even online activities](https://journals.sagepub.com/doi/full/10.1177/1461444819826402?ref=eddieoz.com). This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans. With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior. Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, [they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods](https://www.businessinsider.com/china-social-credit-system-punishments-and-rewards-explained-2018-4?ref=eddieoz.com), or even restricted to making transactions only at stores near their home. Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives. In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms. Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression. ## **DREX and Bill No. 3,341/2024** Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy ([Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG](https://www.camara.leg.br/proposicoesWeb/fichadetramitacao?idProposicao=2259342&fichaAmigavel=nao&ref=eddieoz.com)) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, [Julia drafted her bill, PL No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency. “The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.” ## **Risks and Individual Freedom** Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance. EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited. ## **The Relationship Between DREX and Pix** The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances. ## **International Precedents and Resistance to CBDC** The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations. Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning. ## **Bill No. 3,341/2024 and Popular Pressure** For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill. However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom. ## **What’s at Stake?** Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly. The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way. ## **A Call to Action** The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance. In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also [addressing her Bill No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation. https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0 [(PT-BR version here)](https://www.eddieoz.com/drex-e-o-fim-do-dinheiro-fisico-no-brasil/) ## **What is a CBDC?** Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency. A prominent feature of CBDCs is their **programmability**. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area. In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously. ## **Practical Example: The Case of DREX During the Pandemic** To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, [the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence](https://youtu.be/cjUz2VEk4co?feature=shared&t=484&ref=eddieoz.com), limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice. To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government. ## **How Does China's Social Credit System Work?** Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, [including financial behavior, criminal record, social interactions, and even online activities](https://journals.sagepub.com/doi/full/10.1177/1461444819826402?ref=eddieoz.com). This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans. With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior. Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, [they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods](https://www.businessinsider.com/china-social-credit-system-punishments-and-rewards-explained-2018-4?ref=eddieoz.com), or even restricted to making transactions only at stores near their home. Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives. In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms. Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression. ## **DREX and Bill No. 3,341/2024** Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy ([Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG](https://www.camara.leg.br/proposicoesWeb/fichadetramitacao?idProposicao=2259342&fichaAmigavel=nao&ref=eddieoz.com)) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, [Julia drafted her bill, PL No. 3,341/2024](https://www.camara.leg.br/proposicoesWeb/prop_mostrarintegra?codteor=2473615&filename=Avulso+PL+3341%2F2024&ref=eddieoz.com#:~:text=PROJETO%20DE%20LEI%20N%C2%BA%20....%20%2C%20DE%202024.&text=Congresso%20Nacional%20decreta%3A-,Art.,substitu%C3%ADda%20exclusivamente%20por%20moeda%20digital.), which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency. “The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.” ## **Risks and Individual Freedom** Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance. EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited. ## **The Relationship Between DREX and Pix** The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances. ## **International Precedents and Resistance to CBDC** The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations. Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning. ## **Bill No. 3,341/2024 and Popular Pressure** For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill. However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom. ## **What’s at Stake?** Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly. The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way. ## **A Call to Action** The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance. In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values. @ 592295cf:413a0db9
2024-10-26 13:39:00[Week 21-10] I thinks that Saylor is on right, don't trust verify, is bullshit Bitcoin is a financial tool! I think it's good for me to get away from social media once a week. I could do things outside, like walking. Take pictures of the landscape. The weirdest thing is when the alarm calls you up in an hour. Fiatjaf wants a cache client. I feel like I can do it, I have the set to do it, but nostrudel is no longer working, so it's a little murky. Next nostrudel does not accept changes to settings (It works now!), so maybe i can think something. I want to make a corny chat, test, read this article. Nostr doesn't work with a vpn because relays don't know who you are. jokes aside, some clients have difficulties. ### **I couldn't take pictures of the landscape if I didn't take the wind blades.** Small local controversy. Missing the point of content creator. Simply for final user, Simply for the creator, new feature, no missing nothing. I'm trying to limit everything to writing for a week. I almost did. Maybe another week can do well. Meanwhile I updated apps like Amber and Voyager, coracle, nostrmo. The experiment continues with open vibe following the trending of Nostr. I'm following almost 120 npub. He'll stop, I don't know, possible he's already reached the limit. You still can't block words on the Nostr side of Open, strange thing. The app doesn't count the follow well, still some problem cleaning the cache seems that it doesn't need. After a while open and close and seems updated. I wanted to try open librarian, but I was busy sending fake zap on Nostr. This morning i try and It keeps giving me error 500 when I try to connect to a relay. I hate when a profile follows everyone indistinctly, why does everyone follow? and in voyage, I read with WoT setting, I probably have to do unfollow. There must be an indication in which not include the followers of this person in the web of trust, I would do it by default if you follow more than 600 people. WoT on Nostr Visualized [post on stackernews](https://stacker.news/items/739477)
@ 592295cf:413a0db9
2024-10-26 13:39:00[Week 21-10] I thinks that Saylor is on right, don't trust verify, is bullshit Bitcoin is a financial tool! I think it's good for me to get away from social media once a week. I could do things outside, like walking. Take pictures of the landscape. The weirdest thing is when the alarm calls you up in an hour. Fiatjaf wants a cache client. I feel like I can do it, I have the set to do it, but nostrudel is no longer working, so it's a little murky. Next nostrudel does not accept changes to settings (It works now!), so maybe i can think something. I want to make a corny chat, test, read this article. Nostr doesn't work with a vpn because relays don't know who you are. jokes aside, some clients have difficulties. ### **I couldn't take pictures of the landscape if I didn't take the wind blades.** Small local controversy. Missing the point of content creator. Simply for final user, Simply for the creator, new feature, no missing nothing. I'm trying to limit everything to writing for a week. I almost did. Maybe another week can do well. Meanwhile I updated apps like Amber and Voyager, coracle, nostrmo. The experiment continues with open vibe following the trending of Nostr. I'm following almost 120 npub. He'll stop, I don't know, possible he's already reached the limit. You still can't block words on the Nostr side of Open, strange thing. The app doesn't count the follow well, still some problem cleaning the cache seems that it doesn't need. After a while open and close and seems updated. I wanted to try open librarian, but I was busy sending fake zap on Nostr. This morning i try and It keeps giving me error 500 when I try to connect to a relay. I hate when a profile follows everyone indistinctly, why does everyone follow? and in voyage, I read with WoT setting, I probably have to do unfollow. There must be an indication in which not include the followers of this person in the web of trust, I would do it by default if you follow more than 600 people. WoT on Nostr Visualized [post on stackernews](https://stacker.news/items/739477) @ 8f69ac99:4f92f5fd
2024-10-25 09:49:56O recente relatório do Banco Central Europeu, [*As Consequências Distribucionais do Bitcoin*](https://papers.ssrn.com/sol3/Delivery.cfm/4985877.pdf?abstractid=4985877&mirid=1&type=2), recicla a velha narrativa de que o Bitcoin é um activo especulactivo que causa desigualdade de riqueza sem oferecer benefícios económicos tangíveis. Os autores, Ulrich Bindseil e Jürgen Schaaf, desfilam as críticas de sempre, afirmando que o Bitcoin falhou como sistema de pagamento global e que se transformou numa bolha, enriquecendo os primeiros utilizadores à custa da sociedade. Também lançam uma pitada de alarmismo ambiental e argumentam que o Bitcoin ameaça a democracia. Como era de esperar, o BCE continua apegado às mesmas concepções erradas que já foram desmentidas inúmeras vezes. O que este relatório não percebe, de forma espectacular, é que o Bitcoin não é apenas mais um activo; é uma tábua de salvação para aqueles desiludidos com os sistemas fiduciários inflacionários e governos corruptos. Ao longo desta análise, vamos desmontar os argumentos do BCE, expondo não só o seu profundo desconhecimento sobre o Bitcoin, mas também a ignorância gritante em relação ao seu potencial de conceder soberania financeira a milhões de pessoas em todo o mundo. O BCE retrata o Bitcoin como uma ferramenta elitista, mas ignora como as suas próprias políticas têm sistematicamente enriquecido alguns poucos à custa da maioria. Vamos então entrar no assunto. ### 1. **Deturpam o Papel do Bitcoin como Sistema de Pagamentos** > "O Bitcoin nunca foi usado em grande escala para transacções legais no mundo real." Que originalidade. Os autores descartam a utilidade de pagamento do Bitcoin com um gesto, mostrando que não compreendem a Lightning Network, que facilita transacções rápidas, baratas e escaláveis a nível global. Certamente, talvez os europeus ainda não estejam a comprar os seus cafés com Bitcoin, mas isso é irrelevante. O Bitcoin é uma tábua de salvação financeira em locais como El Salvador e em inúmeras outras regiões que sofrem com sistemas fiduciários em colapso. Esta visão eurocêntrica, como se todo o mundo partilhasse das mesmas condições económicas, reflecte uma total falta de perspectiva. Os autores seleccionam dados a dedo para encaixar na sua narrativa anti-Bitcoin, enquanto convenientemente ignoram os milhões que utilizam o Bitcoin para escapar à hiperinflação e a regimes autoritários. A afirmação de que o Bitcoin não é usado para transacções "legais" é não só enganosa, como revela a sua ignorância sobre as necessidades reais de quem vive fora da sua bolha privilegiada. --- ### 2. **Deturpam o Bitcoin como activo Especulactivo** > "O Bitcoin não gera qualquer fluxo de caixa (como o imobiliário), juros (como as obrigações) ou dividendos (como as ações)." Parabéns, BCE, acabaram de perder o ponto fulcral do Bitcoin. Esta afirmação mostra uma falta de entendimento fundamental do que torna o Bitcoin único. Ao contrário de imóveis ou obrigações, o Bitcoin é uma forma alternativa de dinheiro—não algum esquema de rendimento passivo. O valor do Bitcoin não depende de gerar dividendos ou juros, mas advém da sua escassez, descentralização e resistência à censura. Ao reduzir o Bitcoin a modelos de activos tradicionais, o BCE ignora o paradigma económico revolucionário que este oferece: uma escapatória aos sistemas fiduciários inflacionários, particularmente para os milhares de milhões de pessoas presas em sistemas financeiros corruptos. Ao tentar enquadrar o Bitcoin em modelos convencionais, os autores revelam a sua preguiça intelectual. A utilidade do Bitcoin reside no seu potencial como dinheiro sólido, e não como um veículo de investimento para especuladores atrás de rendimento. --- ### 3. **Deturpam os Custos Ambientais e Sociais da Mineração** > "A mineração de Bitcoin consome muita energia e causa danos ecológicos e sociais." Ah sim, o argumento gasto sobre o consumo energético. Enquanto a mineração de Bitcoin realmente requer energia, os autores omitem convenientemente os enormes avanços que a indústria fez em direcção à sustentabilidade. Cada vez mais, os mineradores de Bitcoin recorrem a fontes de energia renovável e, em alguns casos, estão até a ajudar a financiar infraestruturas de energia verde. A ironia aqui é que o BCE, uma instituição que fomenta políticas que inflam bolhas imobiliárias e de acções, de repente está preocupado com os custos sociais e ambientais. E mais, ignoram como a procura de energia barata por parte do Bitcoin incentiva realmente o desenvolvimento de soluções energéticas sustentáveis. Num mundo onde os sistemas fiduciários alimentam a ganância corporativa e a degradação ambiental, o Bitcoin está posicionado para impulsionar uma verdadeira inovação na energia verde. --- ### 4. **Visão Deturpada da Redistribuição de Riqueza** > "Os efeitos de riqueza do Bitcoin beneficiam os primeiros utilizadores à custa dos que chegam mais tarde e dos que não o possuem." Isto é pura comédia. Aparentemente, o BCE acabou de descobrir que os primeiros investidores em **qualquer** activo beneficiam mais do que os que chegam depois. Não é assim que os mercados funcionam? Os primeiros investidores em acções, imóveis e ouro beneficiam de forma desproporcional—mas, curiosamente, isto só se torna um problema quando se trata de Bitcoin. O que o BCE realmente teme é que o Bitcoin democratize a riqueza de uma maneira que eles não conseguem controlar. Com o Bitcoin, não precisas de acesso privilegiado para participar. Não precisas de um corretor _XPTO_ ou de permissão dos guardiões financeiros. Ao contrário das próprias políticas do BCE—concebidas para inflacionar a riqueza dos já ricos através de bolhas imobiliárias e do mercado de acções—Bitcoin oferece um campo de jogo nivelado para qualquer pessoa com uma ligação à internet. --- ### 5. **Sensacionalismo: a Ameaça à Democracia** > "O aumento perpétuo do preço do Bitcoin empobrece o resto da sociedade e põe em risco a democracia." Aqui, os autores entram no melodrama, avisando que o aumento do preço do Bitcoin põe em risco a democracia. É fascinante como ignoram a verdadeira ameaça à democracia: as suas próprias políticas inflacionárias. Na realidade, os sistemas fiduciários, através da inflação incessante e do _quantitative easing_, erodem sistematicamente a riqueza dos mais pobres e da classe média. Os ricos, com as suas carteiras de acções e imóveis, conseguem resistir à tempestade. Mas o trabalhador comum, cujo salário compra cada vez menos a cada ano, é esmagado. Se há algo que ameaça a democracia, é o poder descontrolado do BCE de desvalorizar a moeda que as pessoas usam para viver. Bitcoin, por outro lado, dá às pessoas uma reserva de valor incorruptível e descentralizada, imune aos caprichos dos banqueiros centrais. --- ### 6. **Percepção "Equivocada" da Escalabilidade do Bitcoin** > "As transações em Bitcoin na blockchain são lentas e caras." Esta crítica ignora a realidade do progresso tecnológico. As transacções on-chain de Bitcoin nunca foram pensadas para compras diárias—para isso é que serve a Lightning Network. Os autores agarram-se a esta crítica desactualizada, como se o Bitcoin fosse uma entidade estática que não evoluiu na última década. Soluções de segunda camada como a Lightning Network permitem transacções quase instantâneas e de baixo custo, tornando o Bitcoin escalável de maneiras que o BCE se recusa a reconhecer. Mas porque deixar que os factos estraguem uma boa história de medo? --- ### 7. **Ignoram o Impacto Económico Global do Bitcoin** > "O Bitcoin não tem casos de uso benéficos para a sociedade." Esta afirmação é tão limitada que é quase impressionante. A utilidade do Bitcoin não se trata de conveniência para os ocidentais comprarem café; trata-se de sobrevivência para as pessoas em países como a Venezuela, o Líbano ou a Nigéria. 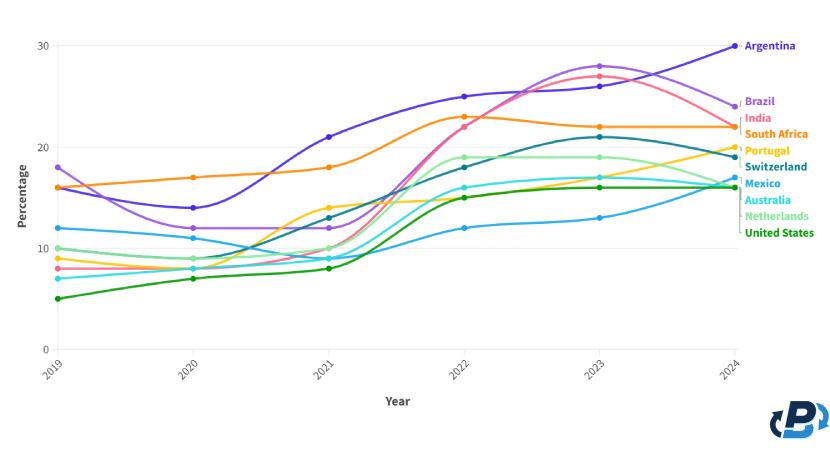 Quando as moedas locais colapsam e as pessoas não podem confiar nos seus bancos, o Bitcoin oferece uma saída. Ao descartar o impacto real de Bitcoin sobre os milhares de milhões (mais de metade da população mundial) de pessoas que vivem sob regimes opressivos e em hiperinflação, o BCE revela um embaraçoso viés ocidental e falta de empatia. O Bitcoin é mais do que apenas um activo alternativo, é uma tábua de salvação para pessoas em todo o mundo que sofrem com sistemas fiduciários falhados. --- ### Conclusão O relatório do BCE recicla críticas desactualizadas e já desmentidas, não conseguindo ver o panorama geral. Aplica modelos financeiros antigos a uma **nova forma de dinheiro**, ignorando o potencial de Bitcoin para democratizar o acesso a um sistema financeiro justo, descentralizado e incorruptível. Enquanto os bancos centrais, como o BCE, continuam a desvalorizar moedas e a inflacionar bolhas de activos (e parece que vem ai mais...), Bitcoin oferece às pessoas um caminho para a soberania financeira. O verdadeiro valor de Bitcoin não se encontra nas críticas superficiais e eurocêntricas do BCE. O seu valor reside na capacidade de fornecer liberdade financeira a indivíduos em todo o mundo, libertos da má gestão de governantes e banqueiros centrais. Se há algo que ameaça a democracia, é o historial do BCE de enriquecer alguns poucos à custa de muitos. Bitcoin, por outro lado, oferece um futuro mais justo—um onde são os indivíduos, e não as instituições, que têm o poder. Alguma literatura: - [Universidade de Cornell - Bitcoin pode impulsionar o desenvolvimento de energias renovaveis](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development) - [Aldeias em Africa com electricidade atraves de Bitcoin](https://gridlesscompute.com/2022/09/28/21st-century-villages/) - [Relatorio de 2023 sobre a Lightning Network da River](https://river.com/learn/files/river-lightning-report-2023.pdf) - [Adopcao de Bitcoin por Pais](https://plasbit.com/blog/bitcoin-adoption-by-country) --- _Photo by [Taras Chernus](https://unsplash.com/@chernus_tr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash]("https://unsplash.com/photos/man-in-teal-hoodie-with-i-love-you-text-euaivxORAm8?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_ #Bitcoin #BCE
@ 8f69ac99:4f92f5fd
2024-10-25 09:49:56O recente relatório do Banco Central Europeu, [*As Consequências Distribucionais do Bitcoin*](https://papers.ssrn.com/sol3/Delivery.cfm/4985877.pdf?abstractid=4985877&mirid=1&type=2), recicla a velha narrativa de que o Bitcoin é um activo especulactivo que causa desigualdade de riqueza sem oferecer benefícios económicos tangíveis. Os autores, Ulrich Bindseil e Jürgen Schaaf, desfilam as críticas de sempre, afirmando que o Bitcoin falhou como sistema de pagamento global e que se transformou numa bolha, enriquecendo os primeiros utilizadores à custa da sociedade. Também lançam uma pitada de alarmismo ambiental e argumentam que o Bitcoin ameaça a democracia. Como era de esperar, o BCE continua apegado às mesmas concepções erradas que já foram desmentidas inúmeras vezes. O que este relatório não percebe, de forma espectacular, é que o Bitcoin não é apenas mais um activo; é uma tábua de salvação para aqueles desiludidos com os sistemas fiduciários inflacionários e governos corruptos. Ao longo desta análise, vamos desmontar os argumentos do BCE, expondo não só o seu profundo desconhecimento sobre o Bitcoin, mas também a ignorância gritante em relação ao seu potencial de conceder soberania financeira a milhões de pessoas em todo o mundo. O BCE retrata o Bitcoin como uma ferramenta elitista, mas ignora como as suas próprias políticas têm sistematicamente enriquecido alguns poucos à custa da maioria. Vamos então entrar no assunto. ### 1. **Deturpam o Papel do Bitcoin como Sistema de Pagamentos** > "O Bitcoin nunca foi usado em grande escala para transacções legais no mundo real." Que originalidade. Os autores descartam a utilidade de pagamento do Bitcoin com um gesto, mostrando que não compreendem a Lightning Network, que facilita transacções rápidas, baratas e escaláveis a nível global. Certamente, talvez os europeus ainda não estejam a comprar os seus cafés com Bitcoin, mas isso é irrelevante. O Bitcoin é uma tábua de salvação financeira em locais como El Salvador e em inúmeras outras regiões que sofrem com sistemas fiduciários em colapso. Esta visão eurocêntrica, como se todo o mundo partilhasse das mesmas condições económicas, reflecte uma total falta de perspectiva. Os autores seleccionam dados a dedo para encaixar na sua narrativa anti-Bitcoin, enquanto convenientemente ignoram os milhões que utilizam o Bitcoin para escapar à hiperinflação e a regimes autoritários. A afirmação de que o Bitcoin não é usado para transacções "legais" é não só enganosa, como revela a sua ignorância sobre as necessidades reais de quem vive fora da sua bolha privilegiada. --- ### 2. **Deturpam o Bitcoin como activo Especulactivo** > "O Bitcoin não gera qualquer fluxo de caixa (como o imobiliário), juros (como as obrigações) ou dividendos (como as ações)." Parabéns, BCE, acabaram de perder o ponto fulcral do Bitcoin. Esta afirmação mostra uma falta de entendimento fundamental do que torna o Bitcoin único. Ao contrário de imóveis ou obrigações, o Bitcoin é uma forma alternativa de dinheiro—não algum esquema de rendimento passivo. O valor do Bitcoin não depende de gerar dividendos ou juros, mas advém da sua escassez, descentralização e resistência à censura. Ao reduzir o Bitcoin a modelos de activos tradicionais, o BCE ignora o paradigma económico revolucionário que este oferece: uma escapatória aos sistemas fiduciários inflacionários, particularmente para os milhares de milhões de pessoas presas em sistemas financeiros corruptos. Ao tentar enquadrar o Bitcoin em modelos convencionais, os autores revelam a sua preguiça intelectual. A utilidade do Bitcoin reside no seu potencial como dinheiro sólido, e não como um veículo de investimento para especuladores atrás de rendimento. --- ### 3. **Deturpam os Custos Ambientais e Sociais da Mineração** > "A mineração de Bitcoin consome muita energia e causa danos ecológicos e sociais." Ah sim, o argumento gasto sobre o consumo energético. Enquanto a mineração de Bitcoin realmente requer energia, os autores omitem convenientemente os enormes avanços que a indústria fez em direcção à sustentabilidade. Cada vez mais, os mineradores de Bitcoin recorrem a fontes de energia renovável e, em alguns casos, estão até a ajudar a financiar infraestruturas de energia verde. A ironia aqui é que o BCE, uma instituição que fomenta políticas que inflam bolhas imobiliárias e de acções, de repente está preocupado com os custos sociais e ambientais. E mais, ignoram como a procura de energia barata por parte do Bitcoin incentiva realmente o desenvolvimento de soluções energéticas sustentáveis. Num mundo onde os sistemas fiduciários alimentam a ganância corporativa e a degradação ambiental, o Bitcoin está posicionado para impulsionar uma verdadeira inovação na energia verde. --- ### 4. **Visão Deturpada da Redistribuição de Riqueza** > "Os efeitos de riqueza do Bitcoin beneficiam os primeiros utilizadores à custa dos que chegam mais tarde e dos que não o possuem." Isto é pura comédia. Aparentemente, o BCE acabou de descobrir que os primeiros investidores em **qualquer** activo beneficiam mais do que os que chegam depois. Não é assim que os mercados funcionam? Os primeiros investidores em acções, imóveis e ouro beneficiam de forma desproporcional—mas, curiosamente, isto só se torna um problema quando se trata de Bitcoin. O que o BCE realmente teme é que o Bitcoin democratize a riqueza de uma maneira que eles não conseguem controlar. Com o Bitcoin, não precisas de acesso privilegiado para participar. Não precisas de um corretor _XPTO_ ou de permissão dos guardiões financeiros. Ao contrário das próprias políticas do BCE—concebidas para inflacionar a riqueza dos já ricos através de bolhas imobiliárias e do mercado de acções—Bitcoin oferece um campo de jogo nivelado para qualquer pessoa com uma ligação à internet. --- ### 5. **Sensacionalismo: a Ameaça à Democracia** > "O aumento perpétuo do preço do Bitcoin empobrece o resto da sociedade e põe em risco a democracia." Aqui, os autores entram no melodrama, avisando que o aumento do preço do Bitcoin põe em risco a democracia. É fascinante como ignoram a verdadeira ameaça à democracia: as suas próprias políticas inflacionárias. Na realidade, os sistemas fiduciários, através da inflação incessante e do _quantitative easing_, erodem sistematicamente a riqueza dos mais pobres e da classe média. Os ricos, com as suas carteiras de acções e imóveis, conseguem resistir à tempestade. Mas o trabalhador comum, cujo salário compra cada vez menos a cada ano, é esmagado. Se há algo que ameaça a democracia, é o poder descontrolado do BCE de desvalorizar a moeda que as pessoas usam para viver. Bitcoin, por outro lado, dá às pessoas uma reserva de valor incorruptível e descentralizada, imune aos caprichos dos banqueiros centrais. --- ### 6. **Percepção "Equivocada" da Escalabilidade do Bitcoin** > "As transações em Bitcoin na blockchain são lentas e caras." Esta crítica ignora a realidade do progresso tecnológico. As transacções on-chain de Bitcoin nunca foram pensadas para compras diárias—para isso é que serve a Lightning Network. Os autores agarram-se a esta crítica desactualizada, como se o Bitcoin fosse uma entidade estática que não evoluiu na última década. Soluções de segunda camada como a Lightning Network permitem transacções quase instantâneas e de baixo custo, tornando o Bitcoin escalável de maneiras que o BCE se recusa a reconhecer. Mas porque deixar que os factos estraguem uma boa história de medo? --- ### 7. **Ignoram o Impacto Económico Global do Bitcoin** > "O Bitcoin não tem casos de uso benéficos para a sociedade." Esta afirmação é tão limitada que é quase impressionante. A utilidade do Bitcoin não se trata de conveniência para os ocidentais comprarem café; trata-se de sobrevivência para as pessoas em países como a Venezuela, o Líbano ou a Nigéria. 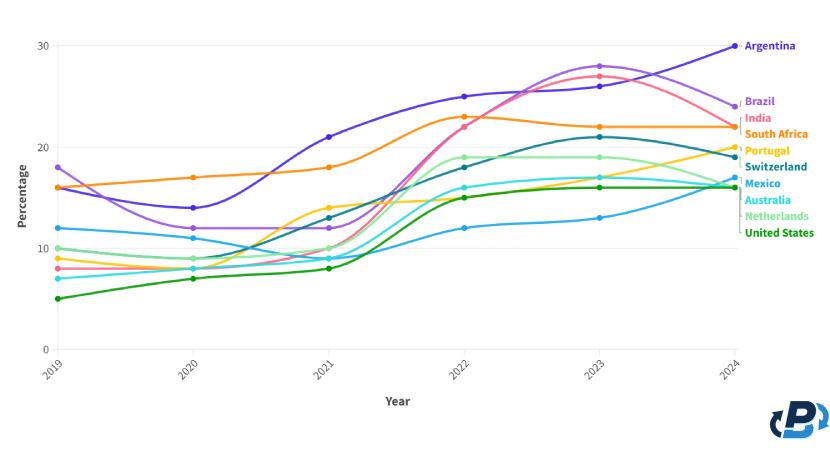 Quando as moedas locais colapsam e as pessoas não podem confiar nos seus bancos, o Bitcoin oferece uma saída. Ao descartar o impacto real de Bitcoin sobre os milhares de milhões (mais de metade da população mundial) de pessoas que vivem sob regimes opressivos e em hiperinflação, o BCE revela um embaraçoso viés ocidental e falta de empatia. O Bitcoin é mais do que apenas um activo alternativo, é uma tábua de salvação para pessoas em todo o mundo que sofrem com sistemas fiduciários falhados. --- ### Conclusão O relatório do BCE recicla críticas desactualizadas e já desmentidas, não conseguindo ver o panorama geral. Aplica modelos financeiros antigos a uma **nova forma de dinheiro**, ignorando o potencial de Bitcoin para democratizar o acesso a um sistema financeiro justo, descentralizado e incorruptível. Enquanto os bancos centrais, como o BCE, continuam a desvalorizar moedas e a inflacionar bolhas de activos (e parece que vem ai mais...), Bitcoin oferece às pessoas um caminho para a soberania financeira. O verdadeiro valor de Bitcoin não se encontra nas críticas superficiais e eurocêntricas do BCE. O seu valor reside na capacidade de fornecer liberdade financeira a indivíduos em todo o mundo, libertos da má gestão de governantes e banqueiros centrais. Se há algo que ameaça a democracia, é o historial do BCE de enriquecer alguns poucos à custa de muitos. Bitcoin, por outro lado, oferece um futuro mais justo—um onde são os indivíduos, e não as instituições, que têm o poder. Alguma literatura: - [Universidade de Cornell - Bitcoin pode impulsionar o desenvolvimento de energias renovaveis](https://news.cornell.edu/stories/2023/11/bitcoin-could-support-renewable-energy-development) - [Aldeias em Africa com electricidade atraves de Bitcoin](https://gridlesscompute.com/2022/09/28/21st-century-villages/) - [Relatorio de 2023 sobre a Lightning Network da River](https://river.com/learn/files/river-lightning-report-2023.pdf) - [Adopcao de Bitcoin por Pais](https://plasbit.com/blog/bitcoin-adoption-by-country) --- _Photo by [Taras Chernus](https://unsplash.com/@chernus_tr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash]("https://unsplash.com/photos/man-in-teal-hoodie-with-i-love-you-text-euaivxORAm8?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash")_ #Bitcoin #BCE