-

@ 2749c032:ef202a37
2025-04-04 08:07:16

send 1k satoshi and send me your email for delivery {please allow delivery to take up to 24hrs max. i'm only 1 man and stay busy offline and i do enjoy my sleep}
originally posted at https://stacker.news/items/934145
-

@ 266815e0:6cd408a5
2025-04-04 07:54:02
This should be published to nostr using nostr-connect account
-

@ 2749c032:ef202a37
2025-04-04 07:51:18
🇨🇦🌎🇺🇸
**ESCROW AVAILABLE **
💳💰🏧🔑💻💵📬
DWVendor
DM for full product list or inquiries
https://t.me/whiteyfrauds
https://x.com/whiteyshub
https://snort.social?ref=undefined
originally posted at https://stacker.news/items/924998
-

@ 3104fbbf:ac623068
2025-04-04 06:58:30

## **Introduction**
If you have a functioning brain, it’s impossible to fully stand for any politician or align completely with any political party. The solutions we need are not found in the broken systems of power but in individual actions and local initiatives. Voting for someone may be your choice, but relying solely on elections every few years as a form of political activism is a losing strategy. People around the world have fallen into the trap of thinking that casting a ballot once every four years is enough, only to return to complacency as conditions worsen. Voting for the "lesser of two evils" has been the norm for decades, yet expecting different results from the same flawed system is naive at best.
The truth is, governments are too corrupt to save us. In times of crisis, they won’t come to your aid—instead, they will tighten their grip, imposing more surveillance, control, and wealth extraction to benefit the oligarch class. To break free from this cycle, we must first protect ourselves individually—financially, geographically, and digitally—alongside our families.
Then, we must organize and build resilient local communities. These are the only ways forward. History has shown us time and again that the masses are easily deceived by the political circus, falling for the illusion of a "savior" who will fix everything. But whether right, center, or left, the story remains the same: corruption, lies, and broken promises. If you possess a critical and investigative mind, you know better than to place your trust in politicians, parties, or self-proclaimed heroes. The real solution lies in free and sovereign individuals who reject the herd mentality and take responsibility for their own lives.
From the beginning of time, true progress has come from individuals who think for themselves and act independently. The nauseating web of politicians, billionaires, and oligarchs fighting for power and resources has never been—and will never be—the answer to our problems. In a world increasingly dominated by corrupted governments, NGOs, and elites, ordinary people must take proactive steps to protect themselves and their families.
---
## **1. Financial Protection: Reclaiming Sovereignty Through Bitcoin**
Governments and central banks have long manipulated fiat currencies, eroding wealth through inflation and bailouts that transfer resources to the oligarch class. Bitcoin, as a decentralized, censorship-resistant, and finite currency, offers a way out. Here’s what individuals can do:
- **Adopt Bitcoin as a Savings Tool**: Shift a portion of your savings into Bitcoin to protect against inflation and currency devaluation.
Bitcoin’s fixed supply (21 million coins) ensures it cannot be debased like fiat money.
- **Learn Self-Custody**: Store your Bitcoin in a hardware wallet or use open-source software wallets. Avoid centralized exchanges, which are vulnerable to government seizure or collapse.
- **Diversify Geographically:** Hold assets in multiple jurisdictions to reduce the risk of confiscation or capital controls. Consider offshore accounts or trusts if feasible.
- **Barter and Local Economies**: In times of crisis, local barter systems and community currencies can bypass failing national systems. Bitcoin can serve as a global medium of exchange in such scenarios.
---
## 2. Geographical Flexibility: Reducing Dependence on Oppressive Systems
Authoritarian regimes thrive on controlling populations within fixed borders. By increasing geographical flexibility, individuals can reduce their vulnerability:
- **Obtain Second Passports or Residencies**: Invest in citizenship-by-investment programs or residency permits in countries with greater freedoms and lower surveillance.
- **Relocate to Freer Jurisdictions**: Research and consider moving to regions with stronger property rights, lower taxes, and less government overreach.
- **Decentralize Your Life**: Avoid keeping all your assets, family, or business operations in one location. Spread them across multiple regions to mitigate risks.
---
## 3. Digital Privacy: Fighting Surveillance with Advanced Tools
The rise of mass surveillance and data harvesting by governments and corporations threatens individual freedom. Here’s how to protect yourself:
- **Use Encryption**: Encrypt all communications using tools like Signal or ProtonMail. Ensure your devices are secured with strong passwords and biometric locks.
- **Adopt Privacy-Focused Technologies**: Use Tor for anonymous browsing, VPNs to mask your IP address, and open-source operating systems like Linux to avoid backdoors.
- **Reject Surveillance Tech**: Avoid smart devices that spy on you (e.g., Alexa, Google Home). Opt for decentralized alternatives like Mastodon instead of Twitter, or PeerTube instead of YouTube.
- **Educate Yourself on Digital Privacy**: Learn about tools and practices that enhance your online privacy and security.
---
## 4. Building Resilient Local Communities: The Foundation of a Free Future
While individual actions are crucial, collective resilience is equally important. Governments are too corrupt to save populations in times of crisis—history shows they will instead impose more control and transfer wealth to the elite.
To counter this, communities must organize locally:
- **Form Mutual Aid Networks**: Create local groups that share resources, skills, and knowledge. These networks can provide food, medical supplies, and security during crises.
- **Promote Local Economies**: Support local businesses, farmers, and artisans. Use local currencies or barter systems to reduce dependence on centralized financial systems.
- **Develop Off-Grid Infrastructure**: Invest in renewable energy, water filtration, and food production to ensure self-sufficiency. Community gardens, solar panels, and rainwater harvesting are excellent starting points.
- **Educate and Empower**: Host workshops on financial literacy, digital privacy, and sustainable living. Knowledge is the most powerful tool against authoritarianism.
---
## 5. The Bigger Picture: Rejecting the Illusion of Saviors
The deep corruption within governments, NGOs, and the billionaire class is evident. These entities will never act in the interest of ordinary people. Instead, they will exploit crises to expand surveillance, control, and wealth extraction. The idea of a political “savior” is a dangerous illusion. True freedom comes from individuals taking responsibility for their own lives and working together to build decentralized, resilient systems.
---
## Conclusion: A Call to Action
The path to a genuinely free humanity begins with individual action. By adopting Bitcoin, securing digital privacy, increasing geographical flexibility, and building resilient local communities, ordinary people can protect themselves against authoritarianism. Governments will not save us—they are the problem. It is up to us to create a better future, free from the control of corrupt elites.
- The tools for liberation already exist.
- The question is: will we use them?
For those interested, I share ideas and solutions in my book « THE GATEWAY TO FREEDOM » https://blisshodlenglish.substack.com/p/the-gateway-to-freedom
⚡ **The time to act is now. Freedom is not given—it is taken.** ⚡
###### If you enjoyed this article, consider supporting it with a Zap!
---
My Substack ENGLISH = https://blisshodlenglish.substack.com/
My substack FRENCH = https://blisshodl.substack.com/
---
Get my Book « THE GATEWAY TO FREEDOM » here 🙏 => https://coinos.io/blisshodl
---
---
-

@ bf95e1a4:ebdcc848
2025-04-04 06:11:18
This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our[ Geyser page](https://geyser.fund/project/infinity)!
## The Gullible Collective
We humans are biased by nature. Everything we think we know is distorted in one way or another by our cognitive shortcomings. The human brain has been forced to evolve and adapt to whatever environment it found itself in over millennia. Having a brain that is capable of setting aside personal aims for the sake of the collective has proven to be advantageous for the evolution of our species as a whole. The same is true for every other social life form. However, letting these parts of our brains guide our political judgment can lead to disastrous results in the long run — not because of bad intentions but because of the simple fact that a few individuals will always thrive by playing every political system for personal gain. From an evolutionary perspective, an army of ay-sayers and martyrs, regardless of whether we’re talking about an army of humans or an army of ants or bacteria, has an advantage over a less disciplined one. From an individual's evolutionary perspective though, it is better to *appear* like you’re a martyr but to run and hide when the actual battle happens. This at least partly explains the high percentage of sociopaths in leadership positions all over the world. If you can appear to act for the good of the collective but dupe your way into more and more power behind people’s backs, you’re more likely to succeed than someone playing a fair game.
The story of banking and fiat currency is a story about collective madness. Historically, rulers have tricked people into killing each other through the promise of an after-life. Through central banking, the rulers of the world wars could trick people into building armies for them by printing more money. This is seldom mentioned in history classes because it still goes on today on a massive scale. Inflation might no longer be paying tank factory workers, but it is the main mechanism that funnels wealth into the pockets of the super-rich and away from everyone else. Inflation is the mechanism that hinders us from transporting the value of our labor through time. It makes us avoid real long-term thinking. We hardly ever consider this a problem because none of us has ever experienced an alternative to it.
Money is still vastly misunderstood by the lion's share of the world’s population. In most parts of the world, banks do something called fractional reserve lending. This means that they lend out money that they don't have — conjuring up new money out of thin air and handing it out to their customers as loans. Loans that have to be paid back with interest. Interest that can’t be paid back with thin air but has to be paid with so-called real money. Real money, of which there isn’t enough around to pay back all the loans, so that a constant need for new credit becomes a crucial part of the entire system. Not to mention central banks, which do the same and worse for governments. We’re so used to it by now that every country is expected to have a national debt. All but a handful of ridiculously rich ones do. National debts are also loans that have to be paid back with interest backed by nothing. Think about that. Your taxes are paying someone else's interest. Your tax money is not paying for your grandmother's bypass operation, it is paying interest to a central bank.
When the ideas of the catholic church ruled Europe, people who didn’t believe in God were few and very seldomly outspoken. They had good reason for this since belief in God was virtually mandatory throughout society. Ever since 1971, when famously dishonest American president Richard Nixon cut the last string that tied the US Dollar to gold, our conception of what the world economy is and ought to be has been skewed by an utterly corrupt system. We’re led to believe that we’re all supposed to work longer and longer days in order to spend more and more money and bury ourselves in more and more debt to keep the machine running. We’re duped into thinking that buying a new car every other year is somehow good for the environment and that bringing a cotton bag to the grocery store will somehow save the planet. Stores manipulate us all the time through advertising and product placement, but we’re led to believe that if we can be “climate-smart,” we’re behaving responsibly. Somehow, our gross domestic product is supposed to increase indefinitely while politicians will save us from ourselves through carbon taxes. Fortunately for us, and unfortunately for them, there now exists a way for unbelievers of this narrative to opt out. Life finds a way, as Jeff Goldblum once so famously put it.
Collectivism has ruined many societies. Those of us fortunate enough to live in liberal democracies tend to forget that even democracy is an involuntary system. It’s often referred to as the “worst form of government except all others that have been tried,” but the system itself is very rarely criticized. We’re so used to being governed that not having a leader seems preposterous to most of us. Still, we pay our taxes, and an enormous cut of the fruit of our labor goes to a third party via inflation and the taxation of every good and service imaginable. Institutions, once in place, tend to always favor their own survival just as much as any other living thing does. People employed in the public sector are unlikely to vote against policies that threaten their livelihood. This is a bigger problem than we realize because it’s subtle and takes a long time, but every democracy is headed in the same direction. A bigger state, a more complicated system, and fewer individual freedoms. Long term, it seems that all of our systems tend to favor those who know how to play that system and not those who contribute the most value to their fellow man. Proponents of socialist policies often claim that failed socialist states “weren’t really socialist” or that “that wasn’t really socialism.” What most people fail to realize is that we’ve never tried real *capitalism* since we’ve always used more or less inflationary currencies. This might very well be the most skewed narrative of our era. We’re all experiencing real, albeit disguised, socialism every single day. True free market capitalism is what we haven’t experienced yet, and it might turn out to be a very different thing than what we’re told to believe that it is by almost all mainstream media.
The validity of the classic right-left scale describing political viewpoints has been debated a lot lately, and alternative scales, like GAL-TAN, the one with an additional Y-axis describing more or less authoritarian tendencies, are popping up in various contexts around the web. After the birth of Bitcoin, there’s a new way to see this. Imagine an origo, a zero point, and a vector pointing to the left of that. *All* politics are arguably on the left because *all* policies need to be funded by taxes, and taxation can be viewed as theft. Taxation can be viewed as theft because, at its core, it’s involuntary. If a person refuses to pay his taxes, there is a threat of violence lurking in the background. Not to mention inflation, which Milton Friedman so elegantly described as “taxation without legislation.” What you do with the portion of your wealth that you have in Bitcoin is another matter altogether. If you take sufficient precautionary privacy measures and you know what you’re doing, your business in Bitcoin is beyond politics altogether. With the introduction of the Lightning Network and other privacy-improving features, it is now impossible for any third party to confiscate your money or even know that you have it, for that matter. This changes the political landscape of every nation on Earth. Bitcoin is much less confiscatable than gold and other scarce assets, which makes it a much better tool for hedging against nation-states. In this sense, Bitcoin obsoletes borders. You can cross any border on Earth with any amount of Bitcoin *in your head*. Think about that! Your Bitcoin exists in every country simultaneously. Any imposed limit on how much money you can carry from one nation to the other is now made obsolete by beautiful mathematics. Bitcoin is sometimes referred to as a “virtual currency.” This is a very inaccurate description. Bitcoin is just mathematics, and mathematics is just about the most real thing there is. There’s nothing virtual about it. Counterintuitive to some, but real nonetheless.
The complexity of human societal hierarchies and power structures is described perfectly in a classic children's book, *The Emperor’s New Clothes*, by Hans Christian Andersen. See the world as the kid who points out that the king is naked in the tale, and everything starts to make sense. Everything in human society is man-made. Nations, leaders, laws, political systems. They’re all castles in the air with nothing but a lurking threat of violence to back them up. Bitcoin is a different beast altogether. It enables every individual to verify the validity of the system at all times. If you really think about it, morality is easy. Don’t hurt other people, and don’t steal other people’s stuff. That’s the basic premise. Humans have but two ways of resolving conflict, conversation and violence, and in this sense, to hurt someone can only mean physical violence. This is why free speech is so important and why you should defend people’s right to speak their minds above everything else. It’s not about being able to express yourself. It’s about your right to hear every side of every argument and thus not have to resort to violence should a conflict of interests occur. You can’t limit free speech with just more speech — there’s always a threat of violence behind the limitations. Code, which both Bitcoin and the Internet are entirely made up of, *is speech*. Any limitations or regulations that your government implements in regard to Bitcoin are not only a display of Bitcoin’s censorship resistance but also a test of your government's stance on freedom of expression. A restriction on Bitcoin use is a restriction on free speech.
Remember, the only alternative to speech that anyone has is violence. Code is a language, mathematics is a language, and money is a linguistic tool. A linguistic tool we use as a means of expressing value to each other and as a way to transport value through space and time. Any restrictions or regulations regarding how you can express value, for example, making it impossible to buy Bitcoin with your credit card, prove that the money you have in your bank account is not really yours. When people realize this, the demand for Bitcoin goes *up*, not down. If you know what you're doing, there’s no need to fear the regulators. They, on the other hand, have good reason to fear an invention that shamelessly breaks their spell.
### **About the Bitcoin Infinity Academy**
The Bitcoin Infinity Academy is an educational project built around [Knut Svanholm](http://primal.net/knut)’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a [video](https://www.youtube.com/@BitcoinInfinityShow) in which Knut and [Luke de Wolf](http://primal.net/luke) discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our [Geyser](https://geyser.fund/project/infinity) page. Signed books, monthly calls, and lots of other benefits are also available.
-

@ 0edc2f47:730cff1b
2025-04-04 03:37:15
## Chef's notes
This started as a spontaneous kitchen experiment—an amalgamation of recipes from old cookbooks and online finds. My younger daughter wanted to surprise her sister with something quick but fancy ("It's a vibe, Mom."), and this is what we came up with. It’s quickly established itself as a go-to favorite: simple, rich, and deeply satisfying. It serves 4 (or 1, depending on the day; I am not here to judge). Tightly wrapped, it will keep up to 3 days in the fridge, but I bet it won't last that long!
## Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 0 min
## Ingredients
- 1 cup (240mL) heavy whipping cream
- 1/4 cup (24g) cocoa powder
- 5 tbsp (38g) Confectioners (powdered) sugar
- 1/4 tsp (1.25mL) vanilla extract (optional)
- Flaky sea salt (optional, but excellent)
## Directions
1. 1. Whip the cream until frothy.
2. 2. Sift in cocoa and sugar, fold or gently mix (add vanilla if using).
3. 3. Whip to medium peaks (or stiff peaks, if that's more your thing). Chill and serve (topped with a touch of sea salt if you’re feeling fancy).
-

@ fd06f542:8d6d54cd
2025-04-04 02:39:25
## 使用nostrbook.com网站
登录和创建用户:

登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。
注册:

可以点击红标位置 生成你的账户。 “确定” 完成注册。
## 创建书籍
### 封面的上传

创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。
或者点击浏览 本地图片文件。
### 标题和作者
正常填写就可以。 书的作者和上传文件人没有一一绑定。
## 写书

创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。
### 列出你创建的所有的书籍

点击图标,就可以进入开始写作了。例如《nostrbook站点日记》

如图所示有4个部分
1. (1)关闭按钮,点击就退出编辑,这时候他会提示你保存,如果不需要保存退出,点击 “不保存退出”
2. (2)`大纲` 是编写 你书籍的大纲,这个参考 docsify文档 下面会有例子。 `时间排列`是 你所有为本书写的章节。但是有些章节你可能废弃了,或者暂时不想展示,都会存在 时间排列里面,就是按照你编写的时间倒序排列的。`草稿` 是你暂时存储的内容,没有上传到网络,存在你本地浏览器的缓存里面。
3. (3)这个部分看到的就是你的章节列表,当让你第一次来的这个地方是空的。`新增章节` 下一次就会有内容了。
4. (4)文件名,是我们存储章节的唯一标识。 `readme.md` 和`_sidebar.md` 是系统默认必须有的。因为docsify技术默认需要这2个。
-

@ c8adf82a:7265ee75
2025-04-04 01:58:49
What is knowledge? Why do we need it?
Since we were small, our parents/guardian put us in school, worked their asses off to give us elective lessons, some get help until college, some even after college and after professional work. Why is this intelligence thing so sought after?
When you were born, you mostly just accepted what your parents said, they say go to school - you go to school, they say go learn the piano - you learn the piano. Of course with a lot of questions and denials, but you do it because you know your parents are doing it for your own good. You can feel the love so you disregard the 'why' and go on with faith
Everything starts with why, and for most people maybe the purpose of knowledge is to be smarter, to know more, just because. But for me this sounds utterly useless. One day I will die next to a man with half a brain and we would feel the same exact thing on the ground. Literally being smarter at the end does not matter at all
However, I am not saying to just be lazy and foolish. For me the purpose of knowledge is action. The more you learn, the more you know what to do, the more you can be sure you are doing the right thing, the more you can make progress on your own being, etc etc
Now, how can you properly learn? Imagine a water bottle. The water bottle's sole purpose is to contain water, but you cannot fill in the water bottle before you open the cap. To learn properly, make sure you open the cap and let all that water pour into you
If you are reading this, you are alive. Don't waste your time doing useless stuff and start to make a difference in your life
Seize the day
-

@ 306555fe:fd7fdf12
2025-04-04 01:37:14
## Blossom Uploader for Nostr
In my mini project to publish from Joplin to Nostr, I wanted to move to publishing images in a Joplin note to some internet file hosting. So the obvious is something like imgur or imgbb and these require account creation and use of an API key.
The nostr way of doing things is to use blossom and your nsec is the authentication, noice!
So I noticed that nostr.build now has a service at https://blossom.band/
It seems to be a very nice service with:
> Backed by the time-proven and highly available infrastructure of Nostr.build,
> with global reach and a fast CDN network.
> Every distinct user's npub gets their own server domain that is not shared by anyone but the
> owner of that npub.
They also have a free tier which is good for experimentation, their paid plans are at https://nostr.build/plans/ . I'm still yet to figure out of they are a candidate for self-hosting or just for media. That's another research project.
Anywayzzz this here article is my test to publish from Joplin for long form posts.
When I was doing wordpress posts, I preferred to write up in Joplin with all its note-taking nice-ness, search, tagging, plugins. I've tried [Habla](https://habla.news/) and [YakiHonne](https://www.yakihonne.com/) but I miss my Joplin workflow and tools. So, I've written this in Joplin and using my plugin to test for the article be uploaded as long form (NIP-23) post.
Still trying to figure out how to get the markdown transferring across cleanly. Sorry, this is a test.
***
---
________
I made a test project to understand Blossom https://github.com/djinoz/blossom_uploader
🙉
Take #2: Explicity set kind:30023
## Blossom Uploader for Nostr
A Node.js command-line tool to upload images and media files to various services compatible with Nostr notes, with full support for the Blossom protocol.
## Installation
```
npm install
```
## Usage
```
node blossom_uploader.js [options] <files...>
```
### Options
- `-s, --service <service>`: Upload service to use (default: "imgbb")
- `-k, --key <key>`: API key for the service (if required)
- `-u, --url <url>`: Custom URL for the service (required for blossom)
- `-n, --nsec <nsec>`: Nostr private key (nsec) for blossom authentication
- `-d, --debug`: Show debug information
- `-o, --output <format>`: Output format: json or url (default: "url")
- `-h, --help`: Display help
- `-V, --version`: Output the version number
### Examples
Upload a single image using ImgBB (default):
```
node blossom_uploader.js path/to/image.jpg
```
Upload using Imgur:
```
node blossom_uploader.js -s imgur image1.png
```
Use your own ImgBB API key:
```
node blossom_uploader.js -s imgbb -k YOUR_API_KEY image.png
```
Upload to a Blossom server using your nsec private key:
```
node blossom_uploader.js -s blossom -u https://blossom.band/upload -n nsec1... image.png
```
Get JSON output:
```
node blossom_uploader.js -o json image.jpg
```
-

@ 6389be64:ef439d32
2025-04-03 21:32:58
Brewing Biology
Episode 1068 of Bitcoin And . . . is LIVE!
This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT.
LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE
The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer.
Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue.
Biochar’s Hidden Superpower: Adsorption & Buffering
Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to:
Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts.
Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs.
Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive.
This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates.
The Carbon Math
Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue.
Tools for the Revolution
The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks.
Bitcoin’s Role in the Loop
Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income.
The Market Potential
Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience.
Why This Matters
This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet.
The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.---
P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting.
You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6
originally posted at https://stacker.news/items/933800
-

@ 2b42dd42:5049393c
2025-04-03 21:25:46
this is a test
<img src="https://blossom.primal.net/5029e2735884c4b18875b1e0e378b91133d6a1118c2cf323eef258467b6932c0.png">
end of the test
-

@ 2ed3596e:98b4cc78
2025-04-03 21:20:27
We’re giving you the chance to win even more sats through the Bitcoin (Wishing) Well—just for telling us what you love about Bitcoin Well.
Each month, when you leave a review for either the Bitcoin Well portal on **Trustpilot** (include your **WellTag**), or our Bitcoin ATMs and (include your **transaction ID and email**), you’ll be entered for a draw where you can win $210 in bitcoin just for sharing your experience!
Whether it’s our self-custody focus, fast Lightning purchases, Lightning referral payouts, private ATM transactions or our unbeatable customer support, we want to hear what makes Bitcoin Well your go-to place for buying, selling, and using bitcoin.
### How to leave your Trustpilot review for our portal
1. Head to our [Trustpilot page](https://ca.trustpilot.com/review/bitcoinwell.com)
2. Write a quick review sharing your favourite Bitcoin Well feature
3. **Include your WellTag (or transaction ID)**, in the review so we can add you to the prize draw
### How to leave your google review for one of our ATMs
1. [Google the Bitcoin Well Bitcoin ATM you recently used](https://www.google.com/search?q=bitcoin+well+atm+near+me&oq=bitcoin+well+atm+near+me+&gs_lcrp=EgZjaHJvbWUqBwgAEAAYgAQyBwgAEAAYgAQyCAgBEAAYFhgeMg0IAhAAGIYDGIAEGIoFMgoIAxAAGIAEGKIEMgoIBBAAGIAEGKIEMgoIBRAAGIAEGKIE0gEIMjM2NWowajeoAgCwAgA&sourceid=chrome&ie=UTF-8)
2. Write a quick review sharing your favourite Bitcoin Well feature
3. **Include your transaction ID**, in the review so we can add you to the prize draw
It’s that easy! Once your review is verified with your welltag or transaction ID, we’ll add your entry to our monthly draw for your chance to win $210 in bitcoin! We’ll announce the winner and the start of each month. Good luck and keep stacking sats!
### What makes Bitcoin Well different
Bitcoin Well is on a mission to enable independence. We do this by making it easy to self custody bitcoin. By custodying their own money, our customers are free to do as they wish without begging for permission. By creating a full ecosystem to buy, sell and use your bitcoin to connect with the modern financial world, you are able to have your cake and eat it too - or have your bitcoin in self custody and easily spend it too 🎂.
[Create your Bitcoin Well account now →](https://app.bitcoinwell.com/signup)
### Invest in Bitcoin Well
We are publicly traded (and love it when our [customers become shareholders!](https://bitcoinwell.com/investors)) and hold ourselves to a high standard of enabling life on a Bitcoin standard. If you want to learn more about Bitcoin Well, please visit our [website](https://bitcoinwell.com/).
-

@ df67f9a7:2d4fc200
2025-04-03 19:54:29
More than just “follows follows” on Nostr, webs of trust algos will ingest increasingly MORE kinds of user generated content in order to map our interactions across the network. Webs of trust will power user discovery, content search, reviews and reccomendations, identity verification, and access to all corners of the Nostr network. Without relying on a central “trust authority” to recommend people and content for us, sovereign Nostr users will make use of “relative trust” scores generated by a wide range of independent apps and services. The problem is, Nostr doesn’t have an opensource library for performing WoT calculations and delivering NIP standard recommendations to users. In order for a “free market” ecosystem of really smart apps and services to thrive, independent developers will need access to extensible “middleware” such as this.
### Project Description
I am building a library for independent developers to offer their own interoperable and configurable WoT services and clients. In addition, and as the primary use case, I am also developing a web client for “in person onboarding” to Nostr, which will make use of this library to provide webs of trust recommendations for “invited” users.
- [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : This is my first project on Nostr, which began a year ago with seed funding from @druid. This web client will leverage “in person” QR invites to generate WoT powered recommendations of follows, apps, and other stuff for new users at their first Nostr touchpoint. The functional MVP release (April ‘25) allows for “instant, anonymous, and fully encrypted” direct messaging and “move in ready” profile creation from a single QR scan.
- [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs)(developer library) : Working with @straycat last fall, I built an opensource and extensible library for Nostr developers to integrate “web of trust” powered reccomendations into their products and services. The real power behind GrapeRank is its “pluggable” interpreter, allowing any kind of content (not just “follows follows”) to be ingested for WoT scoring, and configurable easily by developers as well as end users. This library is currently in v0.1, “generating and storing usable scores”, and doesn’t yet produce NIP standard outputs for Nostr clients.
- [My Grapevine](https://grapevine.my) (algo dashboard) : In addition, I’ve just wrapped up the demo release of a web client by which users and developers can explore the power of the GrapeRank Engine.
### Potential Impact
Webs of Trust is how Nostr scales. But so far, Nostr implementations have been ad-hoc and primarily client centered, with no consistency and little choice for end users. The “onboarding and discovery” tools I am developing promise to :
- Establish sovereignty for webs of trust users (supporting a “free market” of algo choices), with opensource libraries by which any developer can easily implement WoT powered recommendations.
- Accelerate the isolation of bots and bad actors (and improve the “trustiness” of Nostr for everyone else) by streamlining the onboarding of “real world” acquaintances directly into established webs of trust.
- Improve “discoverability of users and content” for any user on any client (to consume and take advantage of WoT powered recommendations for any use case, even as the NIP standards for this are still in flux), by providing an algo engine with “pluggable” inputs and outputs.
- Pave the way for “global Nostr adoption”, where WoT powered recommendations (and searches) are consistently available for every user across a wide variety of clients.
### Timeline & Milestones
2025 roadmap for “Webs of Trust Onboarding and Discovery” :
- [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : MVP release : “scan my QR invite to private message me instantly with a ‘move in ready’ account on Nostr”.
https://nostrmeet.me/
- [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs) (developer library) : 1.0 release : “expanded inputs and output WoT scores to Nostr NIPs and other stuff” for consumption by clients and relays.
https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs
- [My Grapevine](https://grapevine.my) (algo dashboard) : 1.0 release : “algo usage and configuration webapp with API endpoints” for end users to setup GrapeRank scoring for consumption by their own clients and relays.
https://grapevine.my/
- [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : 1.0 release : first GrapeRank integration, offering “follow and app recommendations for invited users”, customizable per-invite for Nostr advocates.
https://nostrmeet.me/
### Prior contributions
- Last spring I hosted panel discussions and [wrote articles on Nostr](https://primal.net/p/npub1manlnflyzyjhgh970t8mmngrdytcp3jrmaa66u846ggg7t20cgqqvyn9tn#reads) exploring how to build “sovereign webs of trust”, where end users can have control over which algorithms to use, and what defines “trust”.
- I contributed [gift wrap encryption](https://github.com/nostr-dev-kit/ndk/commit/82b60c3b6ae2f38bde0e542d31bfa10d58d08116) to NDK.
- I am also authoring [gift wrapped direct messaging and chat room](https://github.com/nostr-dev-kit/ndk/pulls?q=is%3Apr+author%3Amanimejia) modules for NDK.
- Last July, I attended The Bitcoin Conference on an OpenSource pass to raise funds for my onboarding client. I onboarded many Bitcoiners to Nostr, and made valuable connections at Bitcoin Park.
### About Me
I discovered Nostr in September ‘23 as a freelance web developer, after years of looking for a “sovereignty respecting” social media on which to build apps. With this came my first purchase of Bitcoin. By December of that year, I was settled on “open source freedom tech” (Nostr and Bitcoin) as the new direction for my career.
As a web professional for 20+ years, I know the importance of “proof of work” and being connected. For the last 18 months, I have been establishing myself as a builder in this community. This pivot has not been easy, but it has been rewarding and necessary. After so many years building private tech for other people, I finally have a chance to build freedom tech for everyone. I have finally come home to my peeps and my purpose.
Thank you for considering this application for funding.
-

@ 7d33ba57:1b82db35
2025-04-03 17:36:08
Zadar is a coastal city in northern Dalmatia, known for its rich Roman and Venetian history, stunning sunsets, and unique modern attractions like the Sea Organ and Sun Salutation. With ancient ruins, beautiful beaches, and a lively Old Town, Zadar offers a less crowded but equally charming alternative** to Split and Dubrovnik.

## **🏛️ Top Things to See & Do in Zadar**
### **1️⃣ Explore Zadar Old Town 🏰**
- Walk through **narrow, stone-paved streets**, surrounded by **Roman and medieval architecture**.
- Visit **People’s Square (Narodni Trg)** – The **heart of Zadar’s Old Town**, filled with lively cafés.
### **2️⃣ Visit the Sea Organ & Sun Salutation 🎶🌞**
- **Sea Organ** – A one-of-a-kind **musical instrument**, where waves create **natural melodies**.
- **Sun Salutation** – A large **solar-powered light display**, best seen at sunset.
- **Alfred Hitchcock once called Zadar’s sunset “the most beautiful in the world.”** 🌅

### **3️⃣ Admire St. Donatus Church & Roman Forum ⛪**
- **St. Donatus (9th century)** – A unique, round **Byzantine-style church** with great acoustics.
- **Roman Forum** – The remains of an ancient Roman marketplace, built in the **1st century BC**.
### **4️⃣ Climb the Bell Tower of St. Anastasia’s Cathedral 🔔**
- Enjoy **spectacular views** over Zadar’s rooftops and the Adriatic.
- One of the **tallest church towers in Croatia**.

### **5️⃣ Relax at Zadar’s Best Beaches 🏖️**
- **Kolovare Beach** – The most popular **city beach**, just a short walk from the Old Town.
- **Borik Beach** – A **sandy beach with shallow waters**, ideal for families.
- **Punta Bajlo** – A more **natural and peaceful spot**, great for a quiet swim.
### **6️⃣ Take a Day Trip to Kornati National Park ⛵**
- A **beautiful archipelago of 89 islands**, perfect for **boating, swimming, and snorkeling**.
- Join a **boat tour from Zadar** to explore the **untouched nature of the Adriatic**.
### **7️⃣ Try Dalmatian Cuisine 🍽️**
- **Black Risotto (Crni Rižot)** – A delicious squid-ink seafood dish. 🦑
- **Pag Cheese (Paški Sir)** – A famous **sheep’s milk cheese from Pag Island**. 🧀
- **Grilled Adriatic Fish** – Freshly caught and served with **olive oil & Dalmatian herbs**. 🐟

## **🚗 How to Get to Zadar**
✈️ **By Air:**
- **Zadar Airport (ZAD)** is **just 15 minutes from the city center**.
🚘 **By Car:**
- **From Split:** ~1.5 hours (160 km)
- **From Zagreb:** ~2.5 hours (285 km)
🚌 **By Bus:** Regular buses from **Split, Zagreb, Dubrovnik, and Plitvice Lakes**.
⛴️ **By Ferry:** Ferries connect Zadar to nearby islands like **Ugljan, Dugi Otok, and Pašman**.

## **💡 Tips for Visiting Zadar**
✅ **Best time to visit?** **May–October** for warm weather & island trips ☀️
✅ **Stay near the Old Town** – Everything is within walking distance 🏡
✅ **Catch the sunset at the Sea Organ** – It’s a must-do experience 🌊🎶
✅ **Take a ferry to Ugljan Island** for a day of beaches & cycling 🚢🚴♂️
✅ **Book Kornati boat tours in advance** – They sell out fast in summer! ⛵

-

@ 000002de:c05780a7
2025-04-03 17:27:03
### I score zero points. How about you?
https://m.primal.net/QDDi.jpg
I almost called this a boomer test but its more of a Gen X test.
__Credit to Jack Spirko for sharing this on Twitter.__
originally posted at https://stacker.news/items/933537
-

@ 5708b1f6:208df3b8
2025-04-03 15:25:33
The role and significance of music naturally varies from person to person. For some, it is counted among the most important things in life. For others, it may be a superfluous additive of limited value. Due to this difference in perception relating to music, it may be difficult for some individuals to recognize the benefits of compiling a personalized music playlist.
However, the value of music as a therapeutic tool for people already suffering from advanced dementia has been repeatedly demonstrated, and sometimes with astounding, although temporary, results. The internet is full of studies and stories, and YouTube searches yield an abundance of video evidence ranging from clinical studies to anecdotal family recordings of elderly relatives.
All of these data and anecdotes point to a compelling suggestion and an exciting conclusion: music appreciation has tremendous potential as a supplemental activity for mental health maintenance. With insights gained from the study of neuroplasticity, the neurological benefits for musicians and performers are easy to see, but less clear is the fact that mere exposure to music as a casual listener can be of profound psychological importance, even for individuals who don’t consider themselves to be music lovers.
The transformative effect of music is on full display in many of the available videos on YouTube. We can simply search “dementia music,” or ‘Alzheimer’s music” for fast, relevant results. In video after video, we can see elderly subjects who may be slow to speak, detached, disoriented, barely-intelligible, or unresponsive. In care facilities and at gatherings with families, they are interviewed about their youth, and about their feelings related to music.
Many of the videos first show footage of the individual’s normal daily cognitive state, and them listening and responding to the questions, followed by a period of music listening, and then another brief, post-music discussion. The transformation of mental states tends to be very clear when we compare the quality of their cognitive performance before and after the introduction of music. People remark that “a light has been turned back on,” or “his personality returned,” or “it’s as if the person has woken up from sleep.”
Unfortunately, these positive responses are only temporary, and music does not have the power to permanently reverse the symptoms and pathology of advanced dementia and age-related cognitive decline. Also there is no guarantee it will work for every person, or to what degree. Nevertheless, it does not mean that music as therapy is completely without value. In fact, it can be quite the opposite.
When the response is positive, the event can have multiple benefits, and may even be a therapeutic experience for certain listeners. Faces once despondent or vacant become animated and radiant. Long lost smiles return from faraway times and places. Memories and associations from previous ages shake loose and rise to the surface. Many listeners were asked to recount their experiences related to the songs and the time in life with which they were primarily associated. Some of them were able to describe events, places, people, emotions, and reactions with a degree of clarity, dexterity, and articulation that was completely inconsistent with their medical diagnosis and their cognitive performance prior to hearing the music. The song quite literally revives the personality that makes the person, temporarily and superficially reversing the undoing of the mind. For a mind that is coming undone, music as therapy has potential to mitigate suffering and confusion, provide moments of joy and enthusiasm, and ease the transition into and experience of the end-of-life period that awaits all who are fortunate enough to “die of natural causes” in old age.
The benefits described above are specific to “treatment” recipients, but the merit of music as therapy cascades into the lives of everyone involved. Doctors and caretakers are uplifted and encouraged by success stories, which contributes to further proliferation and advancement of music as therapy. More critically, it can have a profound impact on families of dementia patients. In some cases, relatives get a chance to communicate with their loved ones again. Grandchildren have a window of opportunity to learn more, directly from their grandparents, about the youthful experiences and memories of past generations. It’s clear that generational bonds are also strengthened, which can positively impact the future prospects of the young generation as they in turn grow old, and lay new groundwork for generations that follow.
It is unfortunate that some elderly individuals seem to derive less cognitive benefit than others from music therapy. It is not entirely certain why this is so, because there are many factors to consider, but two of the clearest factors are a person’s degree of cognitive decline, and their degree of interest in and enthusiasm for music in general. While these are the most popular metrics by which to judge the potential effectiveness and suitability of music as therapy for a given individual, by far the most important consideration is relevance to each particular person’s life experiences.
This is the opportunity to finally state the obvious: It’s not possible to simply pick any song at random and expect it to have a beneficial effect on the cognitive function of every person who hears it. It’s not as if there’s a Britney Spears song that sparks joy in the heart of every soul on Earth. And the legend of Bill and Ted’s ultimate song that united the world could never be a true story (also because, as we finally learned in 2020, it was not two men and a song that united the world, but rather, the world uniting together to create that song.) However, everyone in the world can make their own playlist custom-tailored to their individual life, experiences, and memories, and some of those playlists might have a song or two by Britney Spears, or even some from one of the “Bill and Ted” soundtracks.
Throughout my decades of music appreciation, an ever-growing level of respect for the enduring spirit of music has overwhelmed me, and it’s clear that no song will ever be loved by all. But every song will be loved by some, certainly at least by someone, or it would cease to exist. This is why a personalized playlist is infinitely more valuable than randomly selected songs, and we can see the truth of this claim upon close examination of recorded interviews with the elderly subjects. The songs that triggered the greatest reactions were songs that interviewees felt strong connections to, based primarily on the song’s associations to the time and place, as well as the emotional context imprinted on the memory of the events surrounding the songs.
This simply means that songs for which we have emotional attachments and vivid memories are songs that invigorate our neural circuits, activating cognitive pathways and opening doors of memory similar to how olfactory sensations can trigger a memory or a sense of déjà vu. There are some exceptions, but a lot of these songs are from a person’s formative years, particularly early developmental years and their teenage period. This comes as no surprise to the discerning neuroplastician, because these are periods of life when neural plasticity is most fluid, neural development and refinement functions are most active and receptive, and the degree of exciting novelty in life tends to be highest when we are young and inexperienced.
Novelty and emotion are critical components of memory formation and whether a given experience will be memorable or not. Something completely new (novelty) can be memorable if it commands your attention, or derails you from your usual pattern of behavior. Similarly, the content of a tedious lecture may be harder to recall without taking notes, while that of an exciting, fun, and funny, interactive lesson has a greater chance of being memorable, and recalled with more clarity and detail (emotion).
When it comes to music, the connection to novelty and emotion is crystal clear. The first time you ever heard that song, it was new and your emotional response was strong. You might even remember the events of that first time you heard it, but not necessarily. Your emotional attachment to the song may have developed later on, when you heard it playing at a party, on one of the most memorable nights of your teenage life, for example. Perhaps it’s just a song (or songs) your parents played a lot when you were young, and it could be a song you yourself heard many times, and looking back realized it holds a special place in your heart, for whatever reason. There are also songs that are special to romantic couples (This song was playing when we…; This is our song; We were together the first time we heard this song; etc.) and these songs, for obvious reasons, can be added to a personalized music playlist at any time in life, as new and old songs take on added personal significance in various ways. There are a multitude of ways that novelty and emotion can combine to form experiences worth remembering, by which memories are made, and if these experiences are imprinted with a musical stamp, the song stamped onto the memory is likely to remain just as memorable as the event itself, and conversely, listening to the song has the potential to vivify the memories and feelings of nostalgia related to the song.
Therefore, as a preventative measure we can implement now, and an insurance policy we may benefit from later, it is advisable that each person should endeavor to compile their own personal, individualized cognitive reserve playlist. When speaking to someone about this idea, they responded, “But what’s the hurry? After all, you’re still quite young.” Just then, it spontaneously occurred to me that a traumatic head injury could befall me the following day or any day hence, and the simple point that “it’s never too early” was well taken.
To create your own cognitive reserve playlist, it is helpful to have a few guiding parameters. Most important of all is to keep an open mind without setting anything in stone. It’s not necessary to finalize the list immediately, if ever. This is a project that deserves your thoughtful consideration, so you deserve to be allowed to take your time. It’s better to get the list populated with your definite favorites, and as many others that come to mind, just to kick-start the process. Besides, due to the virtually infinite number of songs and compositions in existence, we will never be able to make the perfect list in one day, one month, or even one year. We can always revisit the list and make changes later, because our minds cannot retrieve all the data at once. We must go about our business of carrying on, and wait for it to come to us. (It’s guaranteed to be worth the wait, so never fret about it.) You may even find yourself removing one of those “definite favorites” from the list, which is welcome and fine, because it’s not merely a list of your favorite songs. Being a “favorite” is just one of multiple indicators that a song might be appropriate for a cognitive reserve playlist. “Memorable” is another key word.
There are still other factors that determine a song’s suitability for a personal playlist, such as a song that isn’t a personal favorite, but which nevertheless evokes a strong emotional response in some other way. This is best described as nostalgia, and nostalgic emotions are powerful anchors for memories. So any song that arouses some sense of nostalgia also has the power to arouse the memory of events, places, times, and other details tied to that nostalgia. To know what songs are nostalgic for you and add them to your list today, may help you if a time should come that you need music as therapy in order to trigger your memory and cognitive function.
It is because of nostalgia that many songs from our youth are good candidates for inclusion on the playlist. Songs that were popular on the radio or TV when we were children, theme songs from popular television programs that are unforgettable for us, and songs that acted as the soundtrack to our lives, so to speak, while growing into childhood, and then blossoming again from adolescence into adulthood. This period is rich with music of great significance to our personal center.
It is my sincere hope that all people earnestly endeavor to compile their own personalized cognitive reserve playlists, and encourage their loved ones to do the same. Maybe it can help those who suffer to better cope with the condition. Perhaps starting this project now, and focusing on mental health now can be a significant contributing factor to developing robust cognitive reserve in the first place, thereby heading off the worst of what this condition can throw at us, and delaying it until later. And of course, not only should we create the lists, but it’s highly recommended that we also play the songs frequently, and dance to them as well, preferably. It is in the interest of your future health, ability, mobility, enjoyment, and ease of living that I offer this potentially beneficial suggestion, and I am grateful that you have taken the time to hear me out regarding my passion about the restorative and healing properties of music, as they relate to the broader topic of neuroplasticity. So on that note, shall we press play and dance?
-

@ e4950c93:1b99eccd
2025-04-03 14:57:41
Découvrez les matières utilisées ou non dans les produits référencés sur ce site.
### ✅ Matières naturelles
Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire.
#### 🌱 Principaux critères :
- Biodégradabilité
- Non-toxicité
- Présence naturelle et minimum de transformation
#### 🔍 Liste des matières naturelles :
- Caoutchouc naturel
- Chanvre
- Coton
- Cuir
- Liège
- Lin
- Laine
- Soie
- Terre
- … (Autres matières)
⚠️ Bien que naturelles, ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière.
Les versions biologiques, sans traitement chimique… de ces matieres sont privilégiées pour référencer les produits sur ce site.
Les versions "conventionnelles" ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits.
---
### 🚫 Matières non naturelles
Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie.
#### 📌 Principaux problèmes :
- Émissions de microplastiques
- Dépendance aux énergies fossiles
- Mauvaise biodégradabilité
#### 🔍 Liste des matières non naturelles :
- Polyester
- Polyamide
- Acrylique
- Élasthanne
- Viscose
- Silicone
- … (Ajouter les autres matières)
⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque :
- elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et
- aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits.
Dans ce cas, un avertissement est alors affiché sur la fiche du produit.
-

@ e4950c93:1b99eccd
2025-04-03 14:53:56
**Heureu-x-se d’avoir trouvé une information utile sur ce site ?**
Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s.
---
**En bitcoin**
<img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200">
bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d
⚡️`
origin-nature@coinos.io`
---
**En euros, dollars, ou toute autre monnaie prise en charge**
*Promesses uniquement pour le moment :*
<a href="https://liberapay.com/origin-nature/">
<img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200">
</a>
---
Contactez-nous si vous souhaitez faire un don avec toute autre
cryptomonnaie.
---
### 💡 Un modèle de partage de la valeur
La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention.
L’autre moitié permet de couvrir les frais de fonctionnement du site.
-

@ 8671a6e5:f88194d1
2025-04-03 14:52:44
\~ The person came up to me from behind his merchandise stand and saw my Noderunners pin on my black t-shirt, then looked me dead in the eye and asked : “So… what do you sell?”
*This is the eighth long-read in a series of twelve “food for thought” writings on Bitcoin. It was originally meant to be a few chapters in a book, but life’s too short for that.*
## **Define**
Let me start by saying there’s no single way to define or explain a “Bitcoin conference.” The experience can vary depending on a few factors: who’s organizing it (a long-time Bitcoiner or someone from traditional finance trying to grasp Bitcoin), where it’s being held (a sunny paradise like Madeira or a gloomy northern French town), and who’s speaking (technical experts or charismatic entertainers or people with little substance).
Despite these differences, there’s a shared culture that ties these conferences together: a mix of excitement, frustrations, and inevitable evolution. That’s what I explore.
This is just my take, based on what I’ve personally witnessed and what I hear from my surroundings. It’s not meant to be a blanket critique of all Bitcoin conferences as there are plenty I haven’t attended, though I hear about most of them. Even the good ones will evolve into something else over time. So, plan accordingly.
A bit of background on my perspective: at some point in my life, I hit a bump in the road that kept me tied to where I live — a bleak corner of Belgium, surrounded by fiat slaves, shitcoiners, and people who spend six hours a day consuming brain-numbing garbage television. Traveling is an exception for me, but for many Bitcoin conference attendees, it’s a ritual, a must-do event.
So, I view these events with a mix of fascination and grounded skepticism — something I’ve found lacking in many Bitcoiners. I’ve never been to a Bitcoin conference before 2023, despite receiving plenty of invites over the years. From what I heard and saw in photos from friends who attended (even the real early ones) these events seemed eerily similar to the dull hotel conference rooms I once endured in tech and telecom. I’ve had my fill of lukewarm, watery coffee and lifeless speakers droning on about firewalls. So I skipped that particular honor.
Up until around 2018, Bitcoin conferences were a soulless sea of chairs lined up under fluorescent tube lights, draining the life out of attendees—one telecom acronym at a time. Not exactly inviting. Yet, looking back from the perspective of 2025, those were the “pure” days. Back then, people like Roger Ver (before he pivoted to Bitcoin Cash), Andreas Antonopoulos, and encryption specialists spoke to small audiences, explaining Bitcoin in its raw form.
But, like any Bitcoiner, I try to improve myself. So, I made the effort to travel, visit other Bitcoiners, and attend Bitcoin conferences. The conferences I attended in 2023/2024 made me a bit wiser ; not necessarily from what was said on stage (with a few lucky exceptions who still try to bring original thoughts). Most of what I learned came from the long queues, the drama, and watching grifters operate in real time and the good characters floating around.
So, here’s what I’ve learned.
<img src="https://blossom.primal.net/d49fdda9ecb03f04f6c778e5301c67cf2bb15ff3b8647d929cb1755a9f6660a4.png">
**Chain of ticket**
I quickly discovered that many Bitcoin conferences have their own “quest for tickets” dynamic, almost like an industry with its own inner circle. It’s a waterfall system: tickets start at lower prices to fill up the venue (usually right after the previous edition). That’s standard practice, both inside and outside of Bitcoin. But what’s strange is seeing organizations that only pop up when a conference needs promotion—somehow securing tickets for themselves and their friends (or for \*making\* friends) while shilling referral links for small discounts to their followers.
The real free tickets, though, are a hot topic in many local communities and make all the difference for some attendees. What’s particularly interesting is that most ticket prices can be paid in Bitcoin, adding a layer of calculation to the process.
If you paid 230500 sats for your ticket and later see the dollar price fluctuate, say from $180 to $270, or the other way around, by the time the conference starts, you realize you either bought too late or too early.\
It’s better to not have bought at all.
Some ticket holders end up paying less (in dollar terms) than others, making it a gamble. As the event date approaches, ticket prices tend to rise—unless you wait until the last minute, when they haven’t sold out, or just pay at the door. It’s a strange feeling knowing that not everyone paid the same amount (and as mentioned, a significant number get in for free) depending on their timing.
Many organizations and local community representatives show up primarily to be present; securing free tickets, which function more as a badge of recognition than a necessity.\
It’s similar to how a rock groupie sees backstage access: a status symbol, whether for an autograph or something more. Being seen standing next to big names is a huge deal for some, as they derive their own status from proximity.\
This also reinforces the “rockstar status” that conferences create around certain figures, once they come out to take a selfie with some nice people and young fans, then to quickly disappear back to the ‘whale room’ or backstage.
There’s often an entire insider network determining who gets these free tickets. In some cases, it’s naturally tied to the local community, but in others, the professionalism is laughably low. At certain events, you could probably just walk up to the entrance (if there’s even someone checking) and say, “I’m with the organization” to get in for free.
It gets even more absurd.\
At a conference near the French-Swiss border, I was probably one of the very few who actually paid for entry. The real spectacle wasn’t in the talk rooms — which remained eerily empty — but in the dining area, where half the town seemed to have shown up just for the free food. Around 200 people queued for a free lunch, while the presentation halls were at best one-third full throughout the day.
And beyond the ticket games, there are plenty of ways to slip in unnoticed. Carrying a random piece of equipment and mumbling\
“I need to put this crate in the back” can get you past security. Or you can just wait for the one security guard to get distracted by chatting up a girl or stepping out for a smoke, and you’re in. At one event, I walked in alongside someone carrying crates of wine for the VIP lounge. I blended in perfectly (I paid afterward).
So, to sum up: at nearly every conference I’ve been to, a big portion of attendees either walk in for free or hold compensation tickets they got through some connection. Sometimes that connection is uncomfortably close to the organizers. Other times, they just slap an “industry” label on themselves when, in reality, they’re nothing more than a social media bio with a few followers.
Local representatives of a podcast, community, influencer network, or fake marketing club also get in for free. And you? The regular guest, you and I are paying for them. There’s no real vetting process; with some organizers, anyone wearing a Bitcoin t-shirt and saying the magic words “I do community building” or “I know the local Bitcoin meetups” gets a free pass.
The ones who actually want to learn about Bitcoin — the ones who click the link and pay full price — are the ones covering the costs for everyone else and ultimately making these conferences profitable (or at least break even). The problem? They’re the ones left wondering: “Was it really worth my time and money?” only to never return again most of the time.
Because many of the people at these conferences aren’t there to learn. They’re part of the circus. And others? They’re the ones paying for the circus boss, the clowns, and the trapeze artists.
At that one conference with the massive free-lunch crowd, I saw one interesting talk. And I had plenty of valuable conversations and observations — conversations I could have just as easily had by visiting that place outside of a conference setting.
In the end, I realized the main reason I was there was to support a fellow Bitcoiner giving a presentation. And after that? They disappeared from my life. Because, just like in the fiat world, you’re only as good as your last few hours of usefulness to most people.
Which brings me to the next element of Bitcoin conferences...friends
**Bitcoin “frens”**
This might be the hardest lesson of all: you meet fellow Bitcoiners at these conferences. And some of them? They’re truly special characters. A few even made such a deep connection with not-so-well-traveled-me that I would’ve gladly traveled a full travel day just to spend time working and doing something meaningful together (which I actually did).
But most of these connections? They last only a moment. Few survive beyond the conference, mainly because of the vast distances— both in kilometers (or miles) and in the way we live our everyday lives. The Bitcoiners you meet at these events are, for the most part, just regular people trying to make ends meet in the fiat world while saving in Bitcoin. Or they’re chasing the Bitcoin dream or even find a job in the fata morgana of bitcoin jobs. They act like they belong, like a clown acting like he’s going to climb the trapeze.
I respect that. But over time, I realized that many of them operate in Bitcoin mode; a kind of facade. Behind that front, that mask, most are just testing the waters to see if they can make it. And most don’t.\
Treating Bitcoin as a lifestyle movement, a career shortcut, or an identity, has its limits. Eventually, the real person breaks through. And you have to face your own instincts and personality.\
I’ve tried to be an acrobat, and ride the lion, make the audience laugh, but I’m still the seal who’s brought back to the cage after he balanced a ball on his nose. The quote “I’m Jack’s wasted life.” came to mind often when standing somewhere at a conference space.
Self-doubting people stay self-doubting, owning Bitcoin or not. Emotional wrecks remain emotional wrecks — just with Bitcoin now. And when these masks slip off, you’ll see everything: the greed, the overconfidence, the longing for drama, the addictions, the narcissism, the energy-draining personalities, sleaziness usually with the ones who always say the right oneliners or wear the right Bitcoin merch to blend in.
And you can love people for that. Everyone has flaws. Everyone has a price as well.
But these Bitcoin “frens” can also hurt you badly. Because as Bitcoiners, we carry hopes. And hopes are like ants on a sidewalk, they’ll eventually get crushed.\
We long to meet people who see the same truth, the same vision of Bitcoin as we do. Some will act like they actually understand and do, they talk the talk for a while, as if they’re parroting a podcast.
If you stay in the shadows - like I did for years - you won’t have to deal with these things. If you never try, you’ll never be let down. But you still stay in the imaginary basement, letting yourself down. That’s not the bitcoin style. We router around problems. Even if we stand amidst the problems (like a conference).
But if you do? There’s a hefty price to pay — beyond just the money spent. It’s a cost paid in energy, emotions, and social interactions and above all: time.
And once in a while, you’ll meet a friend for life.
Just be prepared:
Bitcoin is a journey that few people you encounter at a conference can take for longer than four years, or even four hours of conversation actually.
And then, after navigating the social maze of Bitcoin conferences —the connections, the masks, the fleeting friendships, the smell of weed and regret — you find yourself facing an even greater challenge: the queue at a coffee stall.
<img src="https://blossom.primal.net/26f00a14b1ff12ea82635f1fd659900a7a836d37591556a31fda91d8210dcff0.png">
##
## \
The Soviet LN Queue
It’s one of the most fascinating and frustrating aspects of every conference: the insanely long lines. Whether it’s for the toilets, a coffee booth, or some niche merchandise stall, you’ll see Bitcoiners waiting like it’s 1963 after a Soviet state bakery just got fresh deliveries.
waiting for coffee Seriously, aren’t we supposed to be the pinnacle of free-market efficiency? Instead, we’ve somehow perfected the art of the long food lines. I remember people waiting in line for like 35 minutes to order a cappuccino!
The usual culprit? A mix of payment chaos and the Bitcoin Orangepill mental issues in action.
A large portion insists on using Lightning (as in "their preferred lighting wallet"), which would be fine except they’re fumbling with some exotic, half-working wallet because using something that’s actually fast might get them sneered at for being “custodial.”
On top of that, vendors are juggling card payments, cash, various Lightning POS systems, and even the occasional cutting edge dudes trying to pay with an Apple Watch or worse, some newly released Lightning-enabled gadget that doesn’t work yet. And when it does work, it requires so much attention and Instagram footage that it takes five minutes just to hand someone a coffee while the guy pays with a lighting NFC ring on his finger, something you can't use ànywhere else ever. It’s cool. But not to anyone else than you.
So, here’s a tip for the regular people, the rats that pay for all of this : sneak out.
Then you find a small, locally owned café outside the conference, pay them in cash, and actually enjoy your food in a few seconds or minutes.
If (and only if) they accept Bitcoin, great! Tip them well. Otherwise, just relax and have a conversation with a local, all the while inside the conference venue there are Bitcoiners filming each other struggling to make a payment with the latest Lightning-enabled NFC card or making the staff uneasy.
Meanwhile, some poor 22-year-old café worker is trapped in an unsolicited podcast participation:
“Wait, you accept tips in Wallet of Satoshi? Who told you that? I’ll explain it to you!”
Or worse:
“Hold on, I just need to do a quick swap… It’s an on-chain transaction, the last block was 19 minutes ago, can’t be long now… wait… umm… do you take VISA?”
At this point, ordering a simple drink at a Bitcoin conference has become an unnecessarily complex, ego-driven performance. With long queues as a direct result. And don’t get me started on the story when 30+ bitcoiners walked in to a Portuguese restaurant without a reservation, and they all wanted to pay with different payment methods. It was like the Vietnam war.
**Solution:**
A tip for conference organizers and their catering : pick one Bitcoin point of sales system, set clear guidelines, and make everyone stick to them. Instruct people to adhere to the following :
Pay with a (bank) card, cash, or Lightning and PLEASE decide beforehand which method you’re using before ordering your stuff! We prefer lighting.
If you’re using Lightning, have enough balance on you wallet or get lost.
Use a compatible wallet. (Provide a tested “approved” list and train staff properly. Users who use other stuff get their order “cancelled” at the first sign of trouble. Your app‘s not scanning, or not compatible, or it has some technical mumbo-jumbo going on to your vpn LN node at home 2000 km away? Please get real and pay with a bank card or something.
No filming, duck-facing (like it's 2017) or stupid selfies with your payment. It’s been done a thousand times by now. There are people in line, waiting behind you, they want to order as well, while you have your little ego trip or marketing moment. Move on please!
“Our staff knows how bitcoin payments work, you don’t need to #orangesplain it to anyone.” We don’t care about your 200th LN app or the latest “but… this one is faster” thingy. Order your drinks, pay and get out of the way please.
Bitcoin fixes many things. But it hasn’t quite fixed this yet.
The bitcoin conference axiom
Going to a conference, versus keeping your bitcoin in your wallet is a tough choice for many.
If you pay nothing for tickets and lodging, while enjoying free meals and cocktails, your opportunity cost drops close to zero —yet your networking and social impact are maximized while you can also do business. That’s ideal. At least, for you. In such case, Bitcoin may only "win" over an extended timeline, but for you, it's essentially a free ride. You incur no real opportunity costs. You drink their milkshake.
On the other hand, if you’re a regular attendee, you pay full price: the ticket, overpriced drinks and food from the stands (losing even more if you generously pay for coffee in sats), plus extras like t-shirts and books (which you’ll never read). Your milkshake gets taken—at least half of it.
If you’re lucky, you might spend an evening in town with the event’s "stars"—those occasional luminaries who briefly grace the normies with their presence for a drink. Some can’t even hold their liquor. Year after year, the same 10 to 15 speakers or panelists appear, funded by your dime, traveling the world and enjoying the perks—some even cultivating fan bases and hosting exclusive parties.
The real opportunity cost hits hardest for regular attendees who come to learn, shelling out significant money while accumulating their fourth hardware wallet or yet another orange-themed t-shirt. They might even squeeze in a selfie with a former sportswear model turned Bitcoiner. For normies (as they’re often called), the financial and social scales rarely tip in their favor.
**Calculating the conference opportunity cost**
To determine the opportunity cost of attending a conference instead of investing in Bitcoin, over time follow these steps:
1. Calculate your total conference expenses, including tickets, travel, food, drinks, and lodging (merchandise and donations).
2. Estimate Bitcoin’s percentage gain over the conference period and the following year(s). (in order to not make you cry, I suggest nog going over 5 years)
3. Multiply your total conference cost by this percentage to determine the potential Bitcoin profit you forgo.
4. Assign a dollar value to the networking or business opportunities you expect to gain from the conference (if you’re not just in it for the laughs, meeting high-class consultants, friendships, self-proclaimed social media Bitcoiners, or the occasional gyrating on one of the musicians/artists/food stall staff members).
5. Subtract this “networking” value from the missed Bitcoin profit to find your net opportunity cost (this is rather personal,… with me it’s zero, but for someone selling t-shirts it’s probably much more).
If the result is negative over the chosen timeframe, the conference was financially worthwhile for you. If positive, holding or buying Bitcoin was the smarter move.
Unless you’re a recognized speaker in this traveling circus, your opportunity cost will likely be positive — meaning all the others lose hard money, while fumbling with your Lightning wallet.
The Conference Opportunity Cost Formula
Let:
CT = Total conference ticket & entrance cost (in dollars)
CR = Total related conference costs (travel, lodging, food, etc.)
C = CT + CR (Total cost)
G = Bitcoin’s % gain per year (as a decimal, e.g., 5% = 0.05)
N = Estimated fiat value of networking/business opportunities and knowledge gained.
### OC = (C × G) − N
Where:
OC (Opportunity Cost) < 0 → The conference was worth attending.
OC (Opportunity Cost) > 0 → Holding/buying Bitcoin was the better move.
Some example calculations (I've left out examples before 2020, I don't want people crying or waking up at night thinking "Why did I go to Amsterdam in 2014?!")
example : Conference in April 2024 Entrance: $200 Lodging, t-shirt, and travel: $900 Bitcoin's estimated gain: 23% (0.23) No business / knowledge value gained OC = (200 + 900) × 0.23 - 0
- $253 OC (Bitcoin would have been the better choice.)
Conference in April 2020 (adjusted for historical Bitcoin growth) Entrance: $175 Lodging and travel: $700 Bitcoin's estimated gain: 1089% (10.89) No business / knowledge value gained OC = (175 + 700) × 10.89 - 0 OC = +$9,529 (Massive missed gains — Bitcoin was the clear winner.
\--
So the first lesson in bitcoin should be: Only attend conferences if you get paid to do so and get a free ticket and free lodging, which kind of would kill that whole industry to begin with.
### Energizing
At first, it’s energizing to meet like-minded bitcoiners, but after a while, you realize that a big chunk of them are just trying to sell you something or aren’t really bitcoin-focused at all. And some of them are just looking for their next way to kill time and boredom.
The drama that comes with attending these conference and the personal interaction can get pretty intense at times, since expectations often don’t match the personalities. Before you know, you’re walking around at night through some bad part of a town, while crying your eyes out because you thought you found your soulmate.
Future pure industry conferences will suffer less from this drama, because everyone there has the same goal — pushing their company or product— while the “other” grassroots conferences are more of a meeting spot for bitcoiners of all types and perspectives, bringing the usual drama and mess that comes with human interactions. Current conferences are a mix of both usually.
I think the current era of bitcoin conferences is coming to an end. Soon, probably by the end of 2025, we’ll see a clear split between industry-driven and human-driven (grassroots) smaller conferences, and it’ll be really important to keep these two separate.
I even had the idea to launch a sort of conference where there wouldn’t be any industry speakers or companies present. Just bitcoiners gathering at a certain place at a specific week and having a good time. I called it “club Sat” And you could just go there, and meet other bitcoiners, while acting there was a big venue and speakers,… but there aren’t any. Would be refreshing. No struggle for tickets, no backstage stuff, no boring talks and presentation,… just the surroundings and the drama lever you want and probably like.
### On stage
The podium is usually left for the known names. Not every conference is like that, but most of them need these names, badly. These names know each other, they encounter one another in VIP rooms and “the industry” a lot of times anyway.
The same people you see in the bitcoin news, the same people having a cult following, and the very same people traveling, staying and drinking for free while spreading the same bitcoin wisdoms will be invited over and over again.
Or… they go rock around as they’re usually so bored they had to start a rock band to entertain themselves. Which is rather entertaining if you’re following up on who does what, but in the end it’s largely just for their own amusement and it shows. I get that. I would do the same. It’s fun and all.
It’s just a bit sad that there are only a small group of top-layer speakers, and then the sub-top that usually has more to say, or gets little opportunity. The reason for that is simple: the “normies” who pay in full for tickets, come there for the “big” names. They don’t know that much about bitcoin usually, so they’re not waiting on some unknown dude explaining something about an obscure niche subject. A debate can help remedie this, to mix it in with some lesser known names, but I have the feeling the current “line-up” of bitcoin conferences feels like a rock festival in 2025 putting the Stone temple pilots or Creed on the card.
Yes, they’ll attract an audience and do their playset well,… but it’s not exactly the pinnacle of the music industry at the moment, neither is Madonna by the way :)
## Promoting anything
The people organizing these events usually aren’t Bitcoiners either — they’re promoters (few exceptions though).
<img src="https://blossom.primal.net/f478bf793b2048a51a15ceab5b8384abdb8d00c6d7c3cdd16731f5379cc1417d.png">
They don’t care if they organize a symposium about a newly discovered STD, A three-day cheese tasting event, a Star Trek convention, or a Lucha Libre wrestling tournament featuring El HODLador, as long as they can sell tickets and make money from merchandise they're good. The last thing on the mind with some of them will be helping bitcoin adoption. There will be a time (soon) where people that know bitcoin, known bitcoiners and know how to organize events get their act together. It will be different than the early days, and it will be different than the boring going-through-the-motions conferences we have now. There shall be fun, social gatherings, life, excitement and culture, and not the “what do you sell?” atmosphere, neither the “this old dude on stage again”?
That’s why they’ll slap any semi-famous name on the poster to pull in a crowd - could be a washed-up Mexican wrestling star with strange legal issues, the cheese-tasting equivalent of Usain Bolt, or your neighborhood Bitcoin old-timer with a beard and a "best selling author" label.
It’s also why most of these conferences end up being more about shitcoins than anything else. And even if they're for the most part about bitcoin, the venue is usually infested with marketing budgets, useless organizations that wanted complimentary tickets (some of them do only one thing: popping up when a conference is nearby and then they’re gone again) ... along with some hawking consultant types you never see anywhere else.
They'll occasionally pay people but usually in fiat, or if you're a bigger name, you might get other deals. For artists or staff, it's all in fiat from what I heard.
Pure Bitcoin conferences, also rely on these big names. Whether it’s a well-known Bitcoiner, a CEO, president, or someone with real reveling knowledge to share with the audience (though that last type is getting rare).
### **Looking for love in all the wrong places**
\
Let’s also address the fair share of “orange diggers” at Bitcoin conferences—because yes, they exist. And no, let’s not single out one particular gender here.
Some people treat a Bitcoin conference like a live-action dating app mixed with a financial vetting process for potential partners. It’s essentially an opportunity to inspect and assess the grab bag of fintech, crypto, and Bitcoin folks in real life.
And if you think this is exaggerated, just attend a few conferences—three is enough. You’ll start noticing the same people popping up, seemingly without any real Bitcoin knowledge, but with a very strong interest in dining, chatting, and generally being around—as long as you look and play the part. I can only imagine how dialed-up this effect must be at a shitcoin conference — probably like flies on a cowpie.
The trick is, in Bitcoin, these people try to blend in. Some even tag along with real Bitcoiners, while others just crash the party and try to get noticed. Their actual interest in Bitcoin? Close to zero. Their main target? Your wallet, or some fantasy thing about getting to know someone out of the ordinary.
And that’s a shame for the people who genuinely care about Bitcoin, who want to network, or who simply are looking for like-minded people. They often find themselves competing for attention with those who’ve turned “being noticed” into a sport, while the rest just wander around, lost in the shuffle. Talk to the quiet ones. Certainly if they look like they belong in a antiques shop.
My advice: Talk to people and be genuine. If you don’t know much about Bitcoin, that’s fine - nobody expects you to be a walking whitepaper and on top of that, most people you'll encounter don't know that much either. It’s bitcoin: we’re all rather average people that hold an extraordinary asset.
Just don’t be "that orange digger" looking for a partner with a loaded bag of bitcoin.
Because in the end, what’s the prize you win? You don’t know who’s under the mask. You don’t even know who’s under your own mask.
Finding a man or woman at a place where half the people are laser-focused on financial sovereignty, and the other half are busy arguing about seed phrase storage, UTXO management, and why your Lightning wallet sucks? But good luck with that. The judge of character usually comes when they find the next shiny object or ditched you standing in the rain at the entrance of a restaurant while dealing with a lightning watchtower or a funny cigarette or whatever.
If you’re truly looking for love, maybe stick to going to a normal bar. If you’re here to learn, connect, and be part of something of a grassroots movement, then be real yourself.
I've seen some rather nasty examples of people at Bitcoin conferences—of all kinds. And I've also seen some really cool examples of truly awesome people. This led me to believe that Bitcoin conferences simply let you meet… people, just dialed up a bit.
Future If you encounter rotten people, they’ll usually be even more rotten than in the fiat world. If you meet really cool people, they’ll be even more awesome than the cool people in the fiat world.
Our volatility is our freedom. So, I guess it’s normal. Doesn’t make it any easier, though.
Bitcoin sees through bullshit, and so do Bitcoiners (even if it takes 21,000 blocks)
Pretty soon, I reckon we’ll see conferences fork into two camps: grass roots, and the “industry” level ones. (human / corporate) I guess I’ll only attend the human part, for sure, but I can’t help but booking myself a single room in a hotel in a nice area in that case, so I don’t have to deal with class of 2022 hippies sharing referral links to their middleman service while asking me for a lighter 3 times in a row. The chances for me of meeting cool bitcoiners in a nearby cocktail bar are a lot higher.
In the meanwhile, I’ll look forward and see how the bitcoin conferences will evolve, fork in two “styles”. One corporate and one underground. Maybe there will be one more genre just for the fun of it.
I’ll stay away, as I don’t like this current mix of industry gigs and having the insiders and “the rest” of us all mingled together clamoring for tickets, attention and coffee. The game is rigged. Staying at home is the better option (for now).
written by AVB
If you like : [tip here](https://coinos.io/allesvoorbitcoin/receive)
-

@ f1989a96:bcaaf2c1
2025-04-03 14:30:08
Good morning, readers!
Georgian officials froze the bank accounts of five nonprofit organizations that provide financial and legal support to detained protesters. This follows rising public unrest as Georgia’s regime pushes new laws restricting free speech and assembly, introducing new fines and penalties, and expanding law enforcement powers. By eroding civil protections, the regime makes it more dangerous and costly for activists, dissenters, and everyday citizens to stand up against an increasingly repressive regime.\
\
Meanwhile, the Indian government introduced a new income tax bill that grants tax authorities sweeping surveillance power over anyone they “suspect” of tax evasion. If suspected, tax authorities are legally allowed to access Indians' email, social media, and bank accounts, raising obvious concerns over state overreach and invasions of individual financial privacy.\
\
In freedom tech news, HRF donated 1 billion satoshis to more than 20 projects worldwide, focusing on supporting human rights defenders and vulnerable communities under authoritarian regimes across Asia, Africa, and Latin America. These gifts advance censorship-resistant communications and transactions, bitcoin education, and privacy tools so that dissidents, nonprofits, and individuals may better protect their human rights and financial freedom. In this letter we also spotlight a new open-source mobile Bitcoin wallet called Cove. While still in beta, the wallet can be used with a hardware device or on its own as a hot wallet, offering a flexible self-custody setup for managing Bitcoin.
We end with a podcast in which HRF Chief Strategy Officer Alex Gladstein discusses the state of freedom tech and why Bitcoin stands as the most promising tool for financial liberation.
**Now, let’s get right to it!**
### [**SUBSCRIBE HERE**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a)
## **GLOBAL NEWS**
#### **Georgia | Officials Freeze Accounts of Organizations Supporting Protesters**
Georgian officials have [frozen](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) the bank accounts of five nonprofit organizations that provide financial and legal aid to dissenters. This comes in response to an uprising of protests over new controversial laws that restrict free expression and assembly, increase fines and detention periods, and expand law enforcement powers. Georgian officials justify the account freezes as part of an investigation into “sabotage,” yet they have provided no evidence. Amnesty International [warns](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) this financial assault could “kill the entire protest movement.” Bitcoin provides a way to circumvent these struggles. Its uncensorable and permissionless nature has helped [sustain](https://www.journalofdemocracy.org/online-exclusive/how-to-dictator-proof-your-money/) pro-democracy movements across Belarus and Nigeria, proving it is capable of addressing the immense financial restrictions dictators impose.
#### **United Arab Emirates | Plans to Launch “Digital Durham” CBDC in 2025**
The United Arab Emirates (UAE) will [launch](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) its central bank digital currency (CBDC), the “[Digital Durham](https://cbdctracker.hrf.org/currency/united-arab-emirates),” by the end of 2025. [According](https://www.ledgerinsights.com/uae-to-launch-cbdc-in-q4-2025/) to the central bank, the CBDC will be available through licensed financial institutions and operate via a government-run digital wallet. Every transaction will be recorded on a permissioned blockchain run by the government. The central bank further [admitted](https://u.ae/en/about-the-uae/strategies-initiatives-and-awards/strategies-plans-and-visions/finance-and-economy/central-bank-digital-currency-strategy) the CBDC will replace cash and [assist](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) law enforcement “by leaving a digital trail for transactions involving illicit funds.” Officials [claim](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) this is to combat financial crime, but it also enables real-time surveillance and tracking of individual financial activity. In a country known for strict laws against dissent and extensive surveillance capabilities, it is not hard to see how a CBDC will erode the autonomy and rights of activists, dissenters, and others who oppose an increasingly authoritarian regime.
#### **India | Grants Tax Authorities Access to Citizens’ Online Data**
Starting in April 2026, the Indian government will [grant](https://economictimes.indiatimes.com/wealth/tax/your-email-and-social-media-account-can-be-accessed-by-income-tax-officer-starting-next-financial-year-in-these-cases/articleshow/118685184.cms) tax authorities legal access to the private online data of any citizen “suspected” of tax evasion. This will include legal access to personal emails, social media, and bank accounts. The new law expands on the Income Tax Act of 1961, which previously limited officials to searching physical premises for financial documents. Now, officials can bypass digital security measures and access private data without consent — all under a legal framework. This dissipation of financial privacy sets an intrusive precedent and opens the door to state-level corruption and surveillance in a country where the Modi regime has already made it clear they are happy to use financial repression to further cement their power.
#### **Myanmar | Bitcoin as a Tool Support Earthquake Disaster Relief**
Last week, a [7.7 magnitude earthquake](https://www.nytimes.com/2025/03/28/world/asia/earthquake-myanmar-thailand-death-toll.html) struck central Burma, with strong tremors reaching neighboring Thailand. The [official death toll ](https://www.reuters.com/business/environment/survivors-myanmar-quake-left-without-food-water-shelter-aid-groups-say-2025-04-01/)has surpassed 2700. And in Bangkok, a 33-story building under construction [collapsed](https://www.youtube.com/watch?v=ynrhyIh4ozo). Despite an already strenuous situation, Burma’s military junta continues its oppression. They are [blocking](https://www.nytimes.com/2025/03/31/world/asia/myanmar-earthquake-rescue.html) rescue teams from reaching the Sagaing region — the epicenter of the earthquake and the heart of Burma’s pro-democracy movement — and instead channeling aid to regime-controlled cities like Naypyidaw and Mandalay. The junta is also continuing to conduct air strikes on civilians and restricting equipment and fuel for aid groups, leaving a [million](https://data.unhcr.org/en/country/mmr) people in Sagaing to fend for themselves. In these repressive circumstances, Bitcoin can provide a censorship-resistant way to send funds directly to those affected.
#### **Angola | Regime Jacks Price of Diesel**
The Angolan regime [raised](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) diesel prices by 50% in the process of eliminating fuel subsidies. Diesel prices suddenly increased from 200 to 300 kwanza per liter, driving up transportation costs in a country where over half the population lives on [less](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) than $2 a day and inflation is over 42%. Previous fuel subsidy cuts in 2023 (where the price of diesel rose [80%](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231)) sparked [protests](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) between taxi drivers, nonprofit workers, and law enforcement. This recent price increase now raises fears of renewed crackdowns. The Angolan regime also introduced new civil society laws that Guilherme Neves, chairman of the human rights organization Associacao Maos Livres, [describes](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) as a “license to erase non-governmental organizations that are not government-compliant.” Angolans find themselves in increasingly precarious financial positions as the government erodes the civil safeguards protecting nonprofits and dissenters.
#### **Nicaragua | Ortega’s Dismantling of Press Freedom**
Since coming to power in 2007, Ortega has [closed or seized](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) 61 media outlets, imprisoned countless journalists, and forced over 280 journalists into exile. His [assault on press freedom](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) has unfolded in two phases: initial raids on local radio stations and TV channels between 2007 and 2017, followed by full-scale censorship in 2018 on independent media outlets like [La Prensa](https://www.laprensani.com/) and [CONFIDENCIAL](https://confidencial.digital/). Ortega then intensified attacks from 2019 to 2021 by closing Nicaragua’s second-oldest newspaper and passing laws to [criminalize](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) free expression. This is a deliberate strategy to eliminate dissent and independent voices. What’s happening in Nicaragua highlights the importance of open and decentralized protocols like nostr, which allow journalists to publish freely without getting censored. While still early, it is becoming essential for sharing information absent the fear of being blocked or silenced by autocratic leaders.
## BITCOIN AND FREEDOM TECH NEWS
#### **HRF | Gifts 1 Billion Satoshis to 20+ Open Source Projects Worldwide**
HRF gifted 1 billion satoshis in its Q1 2025 round of [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) (BDF) grants, supporting more than 20 open-source projects around the world. These projects advance Bitcoin education, open-source software, mining decentralization, and privacy tools for activists contending with authoritarian regimes across Asia, Latin America, and Africa. Supporting permissionless financial tools and censorship-resistant technologies empowers dissidents, journalists, and civil society to organize, transact, and communicate without state suppression and interference. Learn more about the grantees and their work [here](https://hrf.org/latest/hrf-bitcoin-development-fund-supports-20-projects-worldwide/).
#### **Cove | New Open-Source and Permissionless Bitcoin Wallet**
[Cove](https://github.com/bitcoinppl/cove) is a new open-source and permissionless mobile Bitcoin wallet that aims to put users in full control of their Bitcoin. Users can connect their own hardware wallet (to manage Bitcoin offline) or use Cove as a hot wallet (to manage Bitcoin online). It also allows users to create multiple wallets from the app itself. In the future, Cove plans to add Unspent Transaction Output (UTXO) selection and coin control, giving users more independence over their transactions and the tools to better protect their financial privacy. While still in beta and only suitable for test funds, this wallet holds promise as a privacy tool to equip dissidents with self-custodied Bitcoin. You can try it [here](https://github.com/bitcoinppl/cove).
#### **Second | New Ark Implementation Launches on Bitcoin Signet**
[Second](https://second.tech/), a company building on Ark, a protocol designed to help scale Bitcoin’s transaction throughput, [launched](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com) “Bark.” Bark is a test implementation of the Ark protocol deployed on Bitcoin’s [Signet](https://en.bitcoin.it/wiki/Signet) network (where developers test software). More broadly, the Ark protocol helps make Bitcoin transactions more private, faster, and cheaper, supporting the network in handling more transactions and users with the tradeoff of being less trusted than the mainchain, as funds stored in a noncustodial way on Ark can expire if not used. While it is still in early development, the test release of Bark marks a step toward deployment on the main Bitcoin network. Scaling solutions like Ark could be important for activists and individuals. They might ensure Bitcoin remains accessible to all, even as block space demand increases and network fees rise. Learn about it [here](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com).
#### **Braiins | Open Sources Bitcoin Control Board**
[Braiins](https://braiins.com/), a company building tools for Bitcoin mining, [open-sourced](https://x.com/BraiinsMining/status/1904601547855573458) its [BCB100](https://github.com/braiins/BCB100) Bitcoin Control Board, giving miners using their products greater insight and control over their Bitcoin mining hardware and firmware. Sharing the design files and firmware openly helps strengthen Bitcoin’s decentralization, making it more resilient against corporate or state interference. Specifically, open-sourcing mining hardware ensures individual miners can operate independently, reducing censorship risks across the entire network. In turn, this preserves financial freedom by keeping Bitcoin accessible and usable by dissidents, nonprofits, and individuals who need it most.
#### **African Bitcoiners | Publish Bitcoin Starter Guide**
[African Bitcoiners](https://x.com/afribitcoiners) just published “[Bitcoin: Africa’s Guide to Freedom Money](https://x.com/afribitcoiners/status/1904516726273851513),” a Bitcoin guide providing clear, practical insights into how Bitcoin can help people across the continent escape inflation, corrupt regimes, and failing financial systems. It covers essential topics to get started — from choosing a wallet to properly securing Bitcoin. In Africa, where some of the world’s longest-standing dictators restrict even basic financial activity, this guide is a powerful resource for human rights defenders, nonprofits, and everyday citizens. Read it[ here](https://bitcoiners.africa/bitcoin-africas-guide-to-freedom-money/).
#### **OpenSats | 10th Wave of Nostr Grants**
[OpenSats](https://opensats.org/), a nonprofit that supports open-source software development, [announced](https://opensats.org/blog/10th-wave-of-nostr-grants) its tenth wave of grants for projects in the nostr ecosystem. Nostr is a decentralized protocol that enables digital identity and communications outside the reach of authoritarian states. The grant round provides support to nostr Epoxy, which enhances access to nostr by circumventing censorship through a network of paid proxies. This ensures activists and dissidents can continue to communicate even in restrictive environments. Additionally, Zapstore received a grant for providing a permissionless app store built on nostr that enables developers to distribute software without corporate gatekeepers. This provides an open-source alternative to centralized app stores that often comply with government censorship and restrict dissidents’ access to freedom tools.
## RECOMMENDED CONTENT
#### **Freedom Tech with Alex Gladstein**
In this [episode](https://x.com/blockspacepod/status/1896229100702089589?s=46&t=yEPKerGEzeCp5j_mIaNJ8A) of The Gwart Show, Alex Gladstein, chief strategy officer at HRF, breaks down how and why Bitcoin serves as “money dictators can’t stop.” Drawing on more than 17 years of human rights work, he shares real-world examples of activists and citizens using Bitcoin to escape financial repression in authoritarian countries. Gladstein also explores privacy tools, cross-border payments, and why Bitcoin offers promising hope for financial freedom. Watch the full conversation [here](https://www.youtube.com/watch?v=5Ng961QZwI0).
#### **The State of Personal Online Security and Confidentiality with Meredith Whittaker**
In this [keynote](https://www.youtube.com/watch?v=AyH7zoP-JOg) for SXSW 2025, Signal CEO Meredith Whittaker shares her growing concerns around AI, personal data collection, and the erosion of privacy in today’s increasingly digital world. She emphasizes the need for more secure, uncensorable, and privacy-protecting technologies that shield users from surveillance and exploitation, especially in the context of authoritarian regimes. Watch the [full discussion](https://www.youtube.com/watch?v=AyH7zoP-JOg) for a pragmatic view into the future of digital privacy and security.
*If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).*
*Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\
*Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)*
*The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*.
[**Subscribe to newsletter**](http://financialfreedomreport.org/)
[**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Visit our website**](https://hrf.org/programs/financial-freedom/)
-

@ 1aa9ff07:3cb793b5
2025-04-03 14:06:38
In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts.
### **What is Nostr?**
Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays.
Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools.
### **How Does Nostr Work?**
Nostr consists of two main components:
1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools.
2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers.
When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages.
Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network.
### **Advantages of Nostr**
1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another.
2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content.
3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps.
4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks.
### **Use Cases for Nostr**
- **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship.
- **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol.
- **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner.
- **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles.
### **Challenges and Limitations**
While Nostr is a promising technology, it is still in its early stages and faces several challenges:
- **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge.
- **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering.
- **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms.
### **The Future of Nostr**
Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform.
As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring.
### **Conclusion**
Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication.
If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement.
**Understanding Nostr: A Decentralized Social Network Protocol**
In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts.
### **What is Nostr?**
Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays.
Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools.
### **How Does Nostr Work?**
Nostr consists of two main components:
1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools.
2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers.
When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages.
Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network.
### **Advantages of Nostr**
1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another.
2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content.
3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps.
4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks.
### **Use Cases for Nostr**
- **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship.
- **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol.
- **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner.
- **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles.
### **Challenges and Limitations**
While Nostr is a promising technology, it is still in its early stages and faces several challenges:
- **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge.
- **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering.
- **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms.
### **The Future of Nostr**
Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform.
As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring.
### **Conclusion**
Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication.
If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement.
-

@ edeb837b:ac664163
2025-04-03 10:35:59
When it comes to social trading, there are plenty of platforms that claim to offer innovative ways to connect with other traders, share strategies, and improve your market performance. But let's be real: most so-called "social trading" apps are either glorified brokerage platforms with limited community features or outdated, clunky systems that don’t offer real-time value.
There’s really only *one* social trading app you need to consider—**NVSTly**. Here’s why.
## Why NVSTly Stands Above the Rest
NVSTly isn’t just another trading app with a few social features slapped on. It’s **the ultimate [social trading platform](https://nvstly.com)**, purpose-built to empower traders by combining **real-time trade tracking, seamless social sharing, deep market insights, and a powerful trader community.**
Unlike other platforms, NVSTly isn’t just about copying trades or following vague signals—it’s about **true transparency, collaboration, and learning** from top traders in an interactive environment.
## What is NVSTly?
**NVSTly** is a **completely free** social trading platform that lets traders track, share, and analyze their trades in **real time**. Whether you're trading **stocks, options, or crypto**, NVSTly provides a **seamless multi-platform experience**—available via **web, iOS, Android, and even Discord.**
It’s not just a social network—it’s a **trader’s command center** where every trade you make is part of a bigger, smarter ecosystem designed to help you grow.
## Key Features That Make NVSTly #1
### 1. Real-Time Trade Sharing & Tracking
NVSTly integrates with brokers like **Webull** (with more brokerages coming soon) to automatically track your trades and display them in **real-time**. No manual entry—just **instant trade updates** for you and your followers.
### 2. Unique POV Trade Charting
See trades like never before. NVSTly’s proprietary **POV Chart** marks every trade action directly on the candlestick chart, giving you (and your followers) an **unparalleled view of trading strategies in action**.
### 3. Deep Trade Analytics & Trader Dashboards
Get powerful insights into your performance, including:
- **Win rate**
- **Total gain/loss**
- **Average return per trade**
- **Long vs. short ratio**
- **(Coming soon) Drawdown tracking** to measure risk exposure
### 4. Global Trades Feed & Leaderboard
Want to see what the best traders are doing *right now*? The **[Global Trades Feed](https://nvstly.com/trades)** lets you watch live trades, while the **[Leaderboard](https://nvstly.com/trades)** ranks top traders based on performance metrics, making it easy to find successful strategies.
### 5. Fully Integrated with Discord & Telegram
No other platform makes social trading as seamless as NVSTly. The **[NVSTly Discord bot](https://nvstly.com/go/bot)** allows users to:
- **Check a trader’s latest stats**
- **View real-time trade recaps**
- **Fetch charts and ticker data**
- **Receive automated trade notifications**
Telegram users won’t be left out either—NVSTly is working on bringing the same functionality to **Telegram** for even broader access.
### 6. Automated Social Media Sharing
Set your trades to **automatically share** to **Twitter/X, Discord, and soon, Telegram**. Whether you’re growing your personal brand or running a trading community, NVSTly makes sure your trades get noticed.
### 7. Future AI & Machine Learning Enhancements
NVSTly is building **AI-powered trade insights and strategy generation**, allowing traders to:
- **Get automated trading tips** tailored to their strategies
- **Use customizable AI models** to refine their trading approach
- **Interact with a smart AI trading assistant** via the app and Discord bot
## Why NVSTly is the Only Social Trading App You Need
While others might pretend to offer social trading, **NVSTly actually delivers**. It’s not a gimmick or a half-baked feature—it’s a complete **trading ecosystem built for real traders** who want **real-time data, powerful analytics, and a truly social experience.**
With NVSTly, you're not just following traders—you’re **engaging with them, learning from them, and improving your own strategies** in the most **transparent and interactive** way possible.
So don’t waste time on inferior platforms. **NVSTly is the only social trading app that matters.**
## Ready to Take Your Trading to the Next Level?
Join **50,000+ traders** who are already using NVSTly to **track, share, and dominate the markets.**
📲 **Download NVSTly today on [Web](https://nvstly.com), [iOS](https://nvstly.com/go/ios), or [Android](https://nvstly.com/go/android)!**
🚀 **[Join our Discord community](https://nvstly.com/go/discord)** and bring the power of NVSTly straight into your server!
-

@ e4950c93:1b99eccd
2025-04-03 09:55:59
### Équipe Cœur
L'équipe Cœur porte le projet et valide les contenus.
- [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll)
Pour démarrer, je gère le projet en solo. Contactez-moi si vous souhaitez rejoindre l'aventure !
### Enrichisseu-r-se-s de contenus
Les contribut-eur-rice-s rendent ce site vivant et intéressant.
-

@ 77c2969e:a33cfa50
2025-04-03 07:54:55
最近又开始折腾 Technitium DNS Server,发现[之前记录的过程]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)不太完善,于是更新一下。
#### 安装acme.sh
```
curl https://get.acme.sh | sh -s email=youreMailAddress
```
#### 导入环境变量
```
export CF_Token="填API token"
export CF_Zone_ID="填区域ID"
export CF_Account_ID="填账户ID"
```
- Cloudflare 的 API Token 是在 Cloudflare 网页右上角的👤头像--配置文件--API 令牌处创建
- 在 Cloudflare 主页点击你需要使用的域名,下滑到右下角可以看到区域 ID 和账户 ID
### 申请证书
```
acme.sh --issue --dns dns_cf -d dns.235421.xyz
```
- `-d` 后面是你想使用的域名
#### 安装证书
```
acme.sh --install-cert -d dns.235421.xyz \
--key-file /root/certs/key.pem \
--fullchain-file /root/certs/cert.pem \
--reloadcmd "cd /root/certs && openssl pkcs12 -export -out 'dns.pfx' -inkey 'key.pem' -in 'cert.pem' -password pass:1021"
```
- `reloadcmd`是在申请证书之后执行的代码,以后自动更新时也会自动执行这个代码,所以第一次配置好就基本上不用管了。
- `reloadcmd` 中的代码是将 `pem` 格式的证书和密钥转换成一个 `pfx` 格式的证书文件,`-out` 后面是输出的 `pfx` 证书文件名, `-inkey` 和 `-in` 分别是前一步 `acme.sh` 申请的密钥和证书文件。这里必须添加密码,也就是 `1021` 这个,如果不设密码执行命令的话,它会让你交互式输入,但是在自动脚本中就不行。我在前面加了先 `cd` 到证书目录,避免出现问题。
#### 安装 Technitium DNS Server
1. 在[Technitium DNS Server 官网]( https://technitium.com/dns/) 获取安装脚本,也有提供 Docker 镜像以及 Windows 版本。
2. 安装后在 `公网IP:5380` 进入管理界面,首次进入需设置管理员密码,管理员账户默认是 `admin`。
3. 在 `Settings` – `optional protocols` 处开启 DNS over HTTPS ,`TLS Certificate File Path` 处填入转换好的 `pfx` 证书路径,`TLS Certificate Password` 处填你设定的密码,就是我的 `1021` 。
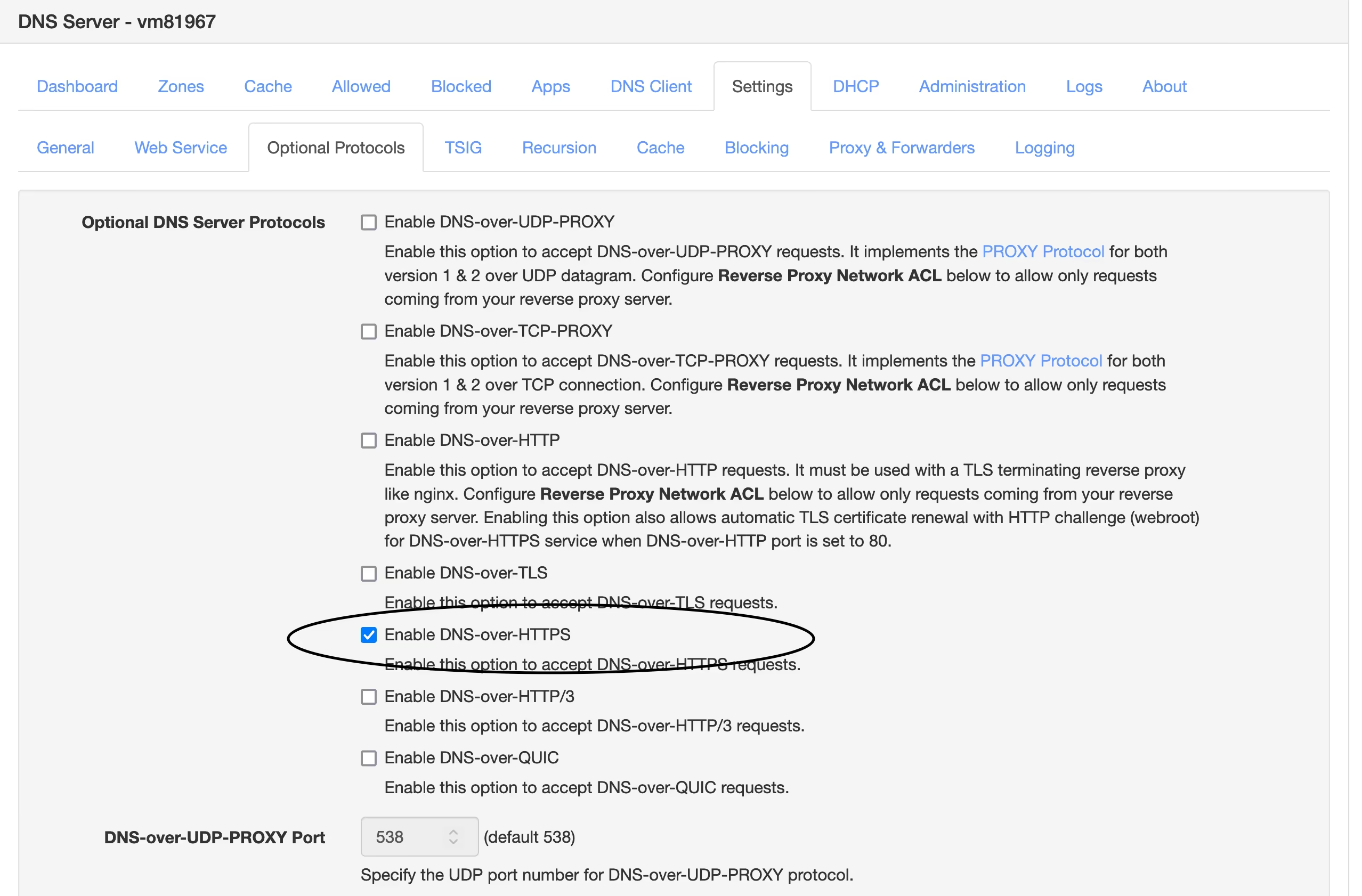
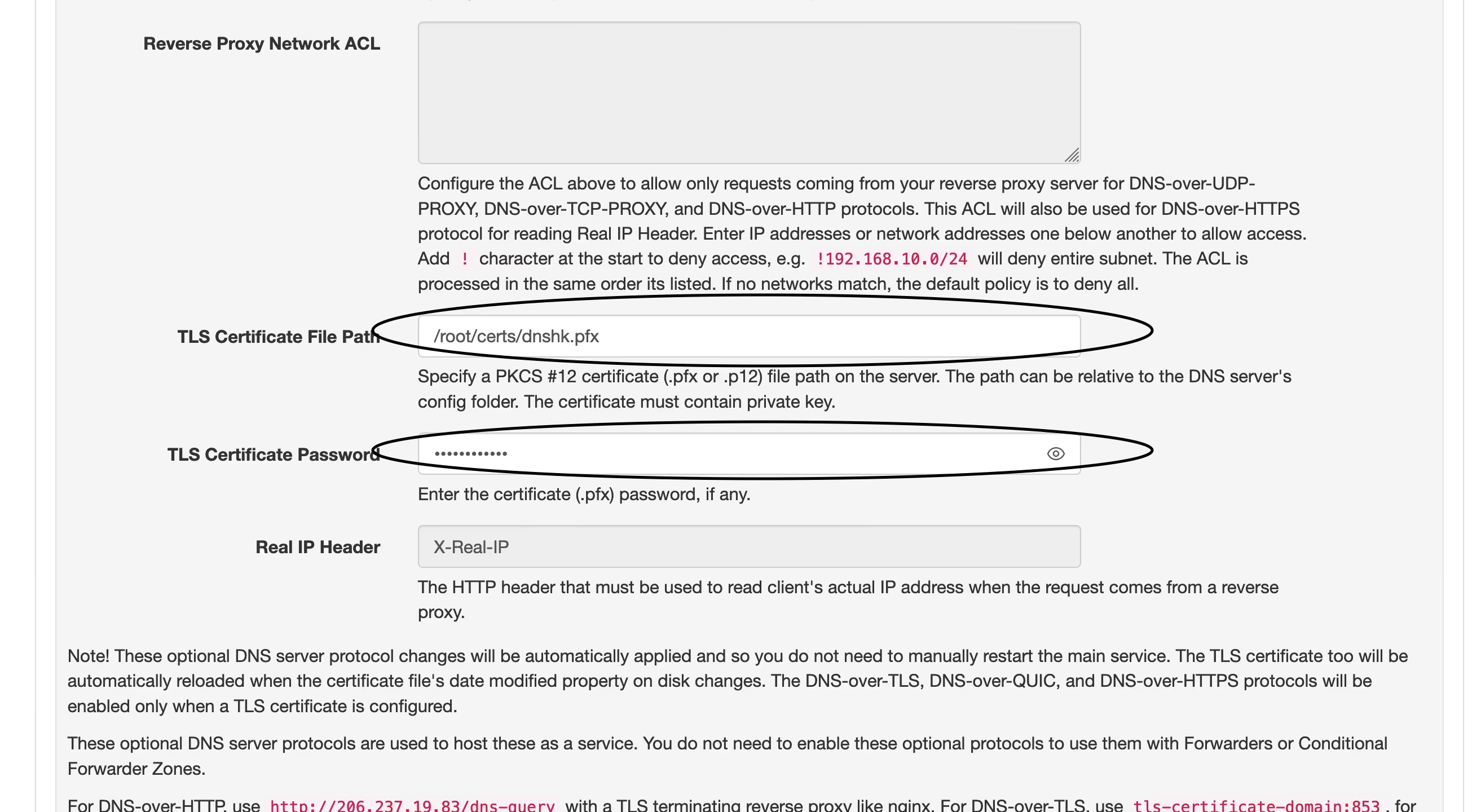
4. 现在打开你的域名,看到如图这样就说明设定成功了,然后在需要设置 DoH 的地方填入 ` https://yourdomain.com/dns-query`即可。
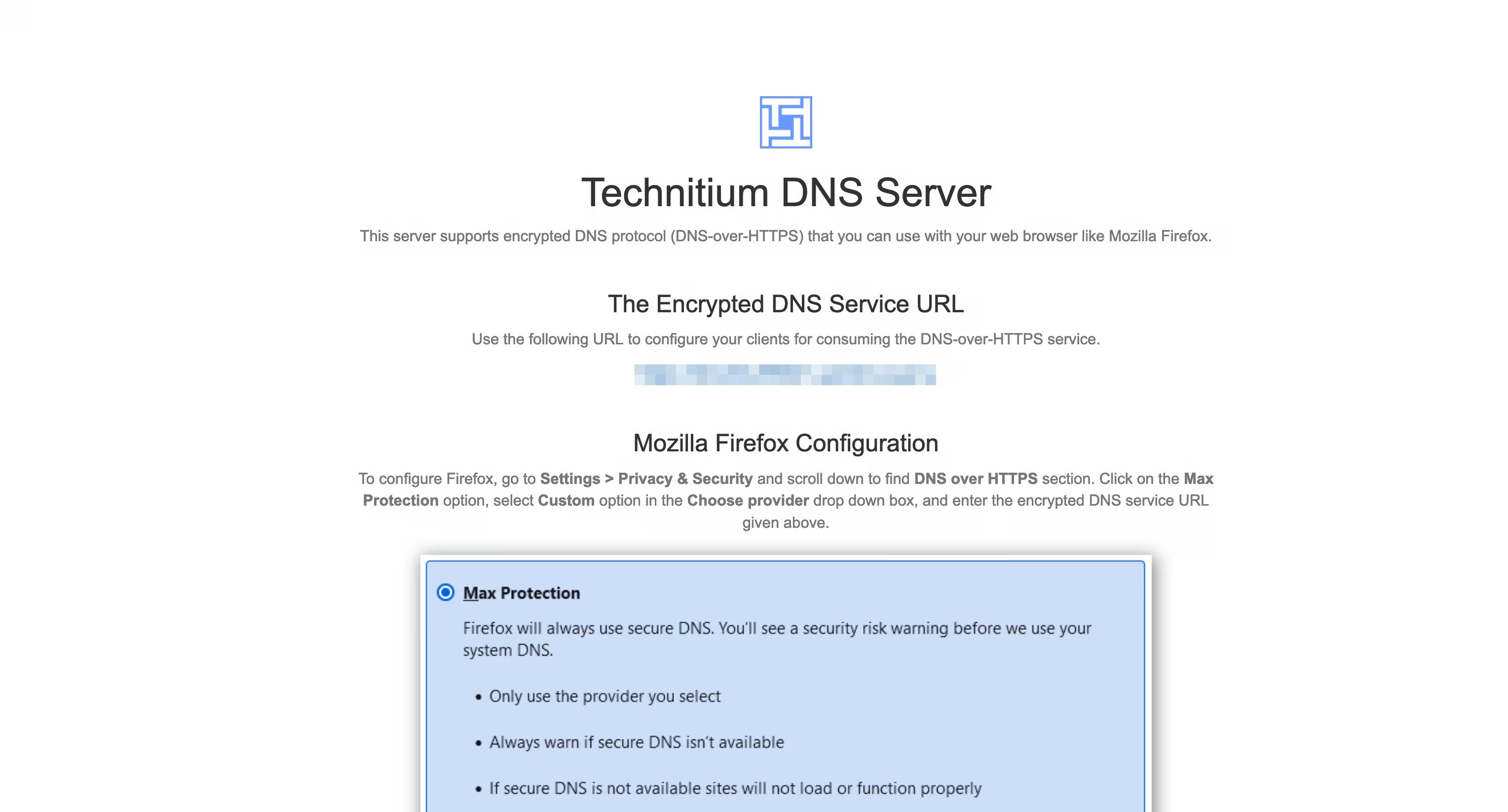
----
我在[之前的文章]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)中使用的是 `DNS over HTTP` 并用 Nginx 反代来实现 `DNS over HTTPS` 的,现在直接用 DoH ,省去了配置 Nginx 的部分,只是多了一步证书格式转换,总体上更简单了。
----
#### 我的设置
- 在`Settings` – `Recursion` 处打开 `Allow Recursion` 以允许递归解析。
- 在`Settings` – `Cache` 处将 `Cache Maximum Entries` 调大些,默认 10000 有点少了。
- 在`Settings` – `General` 处开启 `EDNS Client Subnet (ECS)` 。
- 在`Settings` – `Logging` 处开启 `Use Local Time`。
- 在`Apps` – `App Store` 中安装 `Query Logs (Sqlite)` 以便在 `Logs` – `Query Logs` 处查看 DNS 查询日志。
##### 以下设置可选
- 在`Settings` – `General` 处开启 `Prefer IPv6`
- 在`Settings` – `Web Service` 处为后台管理页面开启 HTTPS,可使用与 DoH 相同的域名和证书,仅端口不同,这个默认 HTTPS 端口是 `53443`。
- 在`Settings` – `Blocking` 处开启拦截功能(默认开启),下面 `Allow / Block List URLs` 可以配置规则,与 AdGuard Home 规则通用,白名单规则须在链接前加上英文叹号 `!`。也可以是本地规则,填路径即可。
- 在`Settings` – `Proxy & Forwarders` 处可以设置上游DNS `Forwarders` 。
-

@ c631e267:c2b78d3e
2025-04-03 07:42:25
**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten.
**Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
**Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
**Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
**Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
**Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
**Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
**In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive.
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]*
*Dazu passend:*
[Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m)
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
-

@ 378562cd:a6fc6773
2025-04-02 22:41:57
Nostr is a decentralized, censorship-resistant social media protocol designed to give users control over online interactions without relying on central authorities. While its architecture offers notable advantages, it also introduces challenges, particularly concerning user anonymity, content moderation, and the dynamics of user influence.
Anonymity and the Risk of Bullying
Nostr's design allows users to create identities without traditional verification methods like email addresses or phone numbers. Instead, users generate a cryptographic key pair: a public key serving as their identifier and a private key for signing messages. This approach enhances privacy but can lead to the "online disinhibition effect," where individuals feel less accountable for their actions due to perceived anonymity. This phenomenon has been linked to increased instances of cyberbullying, as users may engage in behavior online that they would avoid in face-to-face interactions.
Influence Disparities Among Users
In decentralized networks like Nostr, users with larger followings can have a more extensive reach, amplifying their messages across the network. This can create disparities where individuals with thousands of followers wield more influence than those with fewer connections. While this dynamic is not unique to Nostr, the protocol's structure may exacerbate the visibility gap between highly followed users and those with a smaller audience.
Content Moderation and the Challenge of Deletion
Due to Nostr's decentralized nature, content moderation and deletion present significant challenges. Removing content to multiple relays becomes complex once a user posts content to multiple relays, as each relay operates independently. Unlike centralized platforms where a post can be deleted universally, Nostr's architecture means that deleting a post from one relay doesn't ensure its removal from others. This persistence underscores the importance of thoughtful posting, as content may remain accessible indefinitely.
Mitigation Strategies and User Empowerment
Despite these challenges, Nostr offers mechanisms to empower users to manage their experience. Clients can implement features allowing users to mute or block others, tailoring their interactions and content exposure. Additionally, some clients support user-led moderation, enabling individuals to label content as offensive or inappropriate, contributing to a community-driven approach to content management.
In summary, while Nostr's decentralized and anonymous framework promotes freedom and resistance to censorship, it also necessitates a proactive approach from users to navigate challenges related to anonymity, influence disparities, and content permanence. As the platform evolves, ongoing development and community engagement will be crucial in addressing these issues to foster a safe and equitable environment for all participants.
-

@ 5cf42f9d:4465eebf
2025-04-02 21:32:31
-

@ ef53426a:7e988851
2025-04-02 21:02:06
# Bartering and early money
\
Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align.
Enter money. It’s used as an indirect exchange for any goods, so everyone wants it.
Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services.
As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money.
---
# Gold — the basis for sound money
\
Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining).
Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something.
Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money.
---
# Currencies devalued
\
Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire.
The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold.
In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned.
---
# Government-backed money
\
Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies.
By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate.
The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold.
---
# Sound money = functioning economy
\
Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future.
The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events.
---
# Recessions and debt arise from unsound money
\
Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles.
According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt.
We need to return to sound money and a new gold standard. Enter bitcoin.
---
# Bitcoin is scarce
\
Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued.
The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward.
Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released.
That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value.
---
# Bitcoin is secure
\
The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information.
Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power.
Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value.
---
# Challenges for adoption
\
Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value.
Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended.
Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system.
---

This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading).
‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018.
Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop)
-

@ b9f4c34d:7d1a0e31
2025-04-02 20:21:49
<p> ConfirmingDocumentPaid </p>
-

@ 7d33ba57:1b82db35
2025-04-02 19:47:25
Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.

## **🏛️ Top Things to See & Do in Trogir**
### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡**
- Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**.
- Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**.
- Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**.
### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪**
- Offers **stunning panoramic views** over Trogir and the Adriatic.
- A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery!
### **3️⃣ Visit Kamerlengo Fortress 🏰**
- A **15th-century Venetian fortress** with **amazing sea views** from the top.
- In summer, it hosts **concerts and cultural events**.
### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊**
- A lively waterfront filled with **cafés, restaurants, and luxury yachts**.
- Perfect for a **relaxing evening walk** while watching the sunset.

### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️**
- **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities.
- **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**.
- **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation.
### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️**
- A **stunning turquoise bay**, perfect for **swimming and snorkeling**.
- Just **a short boat ride from Trogir**.
### **7️⃣ Try Dalmatian Cuisine 🍽️**
- **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟
- **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi.
- **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.

## **🚗 How to Get to Trogir**
✈️ **By Air:**
- **Split Airport (SPU)** is just **10 minutes away**! 🚕
🚘 **By Car:**
- **From Split:** ~30 minutes (27 km)
- **From Zadar:** ~1.5 hours (130 km)
🚌 **By Bus:** Frequent buses run between **Split and Trogir**.
⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.

## **💡 Tips for Visiting Trogir**
✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️
✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅
✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟
✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤
✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷

-

@ 17538dc2:71ed77c4
2025-04-02 16:04:59
The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised.
### macOS Sequoia 15.4
Released March 31, 2025
Accessibility
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance
AccountPolicy
Available for: macOS Sequoia
Impact: A malicious app may be able to gain root privileges
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24234: an anonymous researcher
AirDrop
Available for: macOS Sequoia
Impact: An app may be able to read arbitrary file metadata
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24097: Ron Masas of BREAKPOINT.SH
App Store
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24276: an anonymous researcher
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24272: Mickey Jin (@patch1t)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A downgrade issue was addressed with additional code-signing restrictions.
CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: A malicious app may be able to read or write to protected files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos.
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A privacy issue was addressed by removing the vulnerable code.
CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk)
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted file may lead to arbitrary code execution
Description: The issue was addressed with improved memory handling.
CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Authentication Services
Available for: macOS Sequoia
Impact: Password autofill may fill in passwords after failing authentication
Description: This issue was addressed through improved state management.
CVE-2025-30430: Dominik Rath
Authentication Services
Available for: macOS Sequoia
Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix
Description: The issue was addressed with improved input validation.
CVE-2025-24180: Martin Kreichgauer of Google Chrome
Authentication Services
Available for: macOS Sequoia
Impact: A malicious app may be able to access a user's saved passwords
Description: This issue was addressed by adding a delay between verification code attempts.
CVE-2025-24245: Ian Mckay (@iann0036)
Automator
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed by removing vulnerable code and adding additional checks.
CVE-2025-30460: an anonymous researcher
BiometricKit
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24237: Yutong Xiu
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A path handling issue was addressed with improved validation.
CVE-2025-30429: Denis Tokarev (@illusionofcha0s)
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with improved checks.
CVE-2025-24212: Denis Tokarev (@illusionofcha0s)
CloudKit
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-24215: Kirin (@Pwnrin)
CoreAudio
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: The issue was addressed with improved checks.
CVE-2025-24163: Google Threat Analysis Group
CoreAudio
Available for: macOS Sequoia
Impact: Playing a malicious audio file may lead to an unexpected app termination
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: This issue was addressed with improved memory handling.
CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia Playback
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: A path handling issue was addressed with improved validation.
CVE-2025-30454: pattern-f (@pattern_F_)
CoreServices
Description: This issue was addressed through improved state management.
CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
CoreText
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Crash Reporter
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher
curl
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-9681
Disk Images
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A file access issue was addressed with improved input validation.
CVE-2025-24255: an anonymous researcher
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-30456: Gergely Kalman (@gergely_kalman)
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24267: an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova
dyld
Available for: macOS Sequoia
Impact: Apps that appear to use App Sandbox may be able to launch without restrictions
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com)
FaceTime
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky)
FeedbackLogger
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved data protection.
CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf)
Focus
Available for: macOS Sequoia
Impact: An attacker with physical access to a locked device may be able to view sensitive user information
Description: The issue was addressed with improved checks.
CVE-2025-30439: Andr.Ess
Focus
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24283: Kirin (@Pwnrin)
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards.
CVE-2025-30461: an anonymous researcher
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was resolved by sanitizing logging
CVE-2025-30447: LFY@secsys from Fudan University
Foundation
Available for: macOS Sequoia
Impact: An app may be able to cause a denial-of-service
Description: An uncontrolled format string issue was addressed with improved input validation.
CVE-2025-24199: Manuel Fernandez (Stackhopper Security)
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2025-30464: ABC Research s.r.o.
CVE-2025-24273: Wang Yu of Cyberserval
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to disclose kernel memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike
Handoff
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-30463: mzzzz__
ImageIO
Available for: macOS Sequoia
Impact: Parsing an image may lead to disclosure of user information
Description: A logic error was addressed with improved error handling.
CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative
Installer
Available for: macOS Sequoia
Impact: An app may be able to check the existence of an arbitrary path on the file system
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Installer
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data
Description: A logic issue was addressed with improved checks.
CVE-2025-24229: an anonymous researcher
IOGPUFamily
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or write kernel memory
Description: An out-of-bounds write issue was addressed with improved input validation.
CVE-2025-24257: Wang Yu of Cyberserval
IOMobileFrameBuffer
Available for: macOS Sequoia
Impact: An app may be able to corrupt coprocessor memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security
Kerberos Helper
Available for: macOS Sequoia
Impact: A remote attacker may be able to cause unexpected app termination or heap corruption
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2025-24235: Dave G.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: The issue was addressed with improved checks.
CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24203: Ian Beer of Google Project Zero
Kernel
Available for: macOS Sequoia
Impact: An attacker with user privileges may be able to read kernel memory
Description: A type confusion issue was addressed with improved memory handling.
CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL
LaunchServices
Available for: macOS Sequoia
Impact: A malicious JAR file may bypass Gatekeeper checks
Description: This issue was addressed with improved handling of executable types.
CVE-2025-24148: Kenneth Chew
libarchive
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-48958
Libinfo
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: An integer overflow was addressed with improved input validation.
CVE-2025-24195: Paweł Płatek (Trail of Bits)
libnetcore
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may result in the disclosure of process memory
Description: A logic issue was addressed with improved checks.
CVE-2025-24194: an anonymous researcher
libxml2
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2025-27113
CVE-2024-56171
libxpc
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed through improved state management.
CVE-2025-24178: an anonymous researcher
libxpc
Available for: macOS Sequoia
Impact: An app may be able to delete files for which it does not have permission
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc)
libxpc
Available for: macOS Sequoia
Impact: An app may be able to gain elevated privileges
Description: A logic issue was addressed with improved checks.
CVE-2025-24238: an anonymous researcher
Mail
Available for: macOS Sequoia
Impact: "Block All Remote Content" may not apply for all mail previews
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24172: an anonymous researcher
manpages
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30450: Pwn2car
Maps
Available for: macOS Sequoia
Impact: An app may be able to read sensitive location information
Description: A path handling issue was addressed with improved logic.
CVE-2025-30470: LFY@secsys from Fudan University
NetworkExtension
Available for: macOS Sequoia
Impact: An app may be able to enumerate a user's installed apps
Description: This issue was addressed with additional entitlement checks.
CVE-2025-30426: Jimmy
Notes
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24262: LFY@secsys from Fudan University
NSDocument
Available for: macOS Sequoia
Impact: A malicious app may be able to access arbitrary files
Description: This issue was addressed through improved state management.
CVE-2025-24232: an anonymous researcher
OpenSSH
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An injection issue was addressed with improved validation.
CVE-2025-24246: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24261: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A logic issue was addressed with improved checks.
CVE-2025-24164: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: A malicious app with root privileges may be able to modify the contents of system files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0)
Parental Controls
Available for: macOS Sequoia
Impact: An app may be able to retrieve Safari bookmarks without an entitlement check
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24259: Noah Gregory (wts.dev)
Photos Storage
Available for: macOS Sequoia
Impact: Deleting a conversation in Messages may expose user contact information in system logging
Description: A logging issue was addressed with improved data redaction.
CVE-2025-30424: an anonymous researcher
Power Services
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24173: Mickey Jin (@patch1t)
Python
Available for: macOS Sequoia
Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2023-27043
RPAC
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved validation of environment variables.
CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to user interface spoofing
Description: The issue was addressed with improved UI.
CVE-2025-24113: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to address bar spoofing
Description: The issue was addressed with improved checks.
CVE-2025-30467: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: A website may be able to access sensor information without user consent
Description: The issue was addressed with improved checks.
CVE-2025-31192: Jaydev Ahire
Safari
Available for: macOS Sequoia
Impact: A download's origin may be incorrectly associated
Description: This issue was addressed through improved state management.
CVE-2025-24167: Syarif Muhammad Sajjad
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access removable volumes without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit)
Sandbox
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: The issue was addressed with improved checks.
CVE-2025-30452: an anonymous researcher
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24181: Arsenii Kostromin (0x3c3e)
SceneKit
Available for: macOS Sequoia
Impact: An app may be able to read files outside of its sandbox
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30458: Mickey Jin (@patch1t)
Security
Available for: macOS Sequoia
Impact: A remote user may be able to cause a denial-of-service
Description: A validation issue was addressed with improved logic.
CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington
Security
Available for: macOS Sequoia
Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data
Description: This issue was addressed with improved access restrictions.
CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog)
Share Sheet
Available for: macOS Sequoia
Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started
Description: This issue was addressed with improved access restrictions.
CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: A permissions issue was addressed with improved validation.
CVE-2025-30465: an anonymous researcher
Shortcuts
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24280: Kirin (@Pwnrin)
Shortcuts
Available for: macOS Sequoia
Impact: A Shortcut may run with admin privileges without authentication
Description: An authentication issue was addressed with improved state management.
CVE-2025-31194: Dolf Hoegaerts
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: This issue was addressed with improved access restrictions.
CVE-2025-30433: Andrew James Gonzalez
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk)
Siri
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-24217: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A privacy issue was addressed by not logging contents of text fields.
CVE-2025-24214: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to enumerate devices that have signed into the user's Apple Account
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L
Siri
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An authorization issue was addressed with improved state management.
CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Siri
Available for: macOS Sequoia
Impact: An attacker with physical access may be able to use Siri to access sensitive user data
Description: This issue was addressed by restricting options offered on a locked device.
CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security
SMB
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: The issue was addressed with improved memory handling.
CVE-2025-24269: Alex Radocea of Supernetworks
SMB
Available for: macOS Sequoia
Impact: Mounting a maliciously crafted SMB network share may lead to system termination
Description: A race condition was addressed with improved locking.
CVE-2025-30444: Dave G.
SMB
Available for: macOS Sequoia
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL
smbx
Available for: macOS Sequoia
Impact: An attacker in a privileged position may be able to perform a denial-of-service
Description: The issue was addressed with improved memory handling.
CVE-2025-24260: zbleet of QI-ANXIN TianGong Team
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Software Update
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24254: Arsenii Kostromin (0x3c3e)
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
StickerKit
Available for: macOS Sequoia
Impact: An app may be able to observe unprotected user data
Description: A privacy issue was addressed by moving sensitive data to a protected location.
CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania
Storage Management
Available for: macOS Sequoia
Impact: An app may be able to enable iCloud storage features without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A race condition was addressed with additional validation.
CVE-2025-24240: Mickey Jin (@patch1t)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to bypass Privacy preferences
Description: A race condition was addressed with additional validation.
CVE-2025-31188: Mickey Jin (@patch1t)
Summarization Services
Available for: macOS Sequoia
Impact: An app may be able to access information about a user's contacts
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk)
System Settings
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24278: Zhongquan Li (@Guluisacat)
System Settings
Available for: macOS Sequoia
Impact: An app with root privileges may be able to access private information
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
SystemMigration
Available for: macOS Sequoia
Impact: A malicious app may be able to create symlinks to protected regions of the disk
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30457: Mickey Jin (@patch1t)
Voice Control
Available for: macOS Sequoia
Impact: An app may be able to access contacts
Description: This issue was addressed with improved file handling.
CVE-2025-24279: Mickey Jin (@patch1t)
Web Extensions
Available for: macOS Sequoia
Impact: An app may gain unauthorized access to Local Network
Description: This issue was addressed with improved permissions checking.
CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven
Web Extensions
Available for: macOS Sequoia
Impact: Visiting a website may leak sensitive data
Description: A script imports issue was addressed with improved isolation.
CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: The issue was addressed with improved memory handling.
WebKit Bugzilla: 285892
CVE-2025-24264: Gary Kwong, and an anonymous researcher
WebKit Bugzilla: 284055
CVE-2025-24216: Paul Bakker of ParagonERP
WebKit
Available for: macOS Sequoia
Impact: A type confusion issue could lead to memory corruption
Description: This issue was addressed with improved handling of floats.
WebKit Bugzilla: 286694
CVE-2025-24213: Google V8 Security Team
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected process crash
Description: A buffer overflow issue was addressed with improved memory handling.
WebKit Bugzilla: 286462
CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: A use-after-free issue was addressed with improved memory management.
WebKit Bugzilla: 285643
CVE-2025-30427: rheza (@ginggilBesel)
WebKit
Available for: macOS Sequoia
Impact: A malicious website may be able to track users in Safari private browsing mode
Description: This issue was addressed through improved state management.
WebKit Bugzilla: 286580
CVE-2025-30425: an anonymous researcher
WindowServer
Available for: macOS Sequoia
Impact: An attacker may be able to cause unexpected app termination
Description: A type confusion issue was addressed with improved checks.
CVE-2025-24247: PixiePoint Security
WindowServer
Available for: macOS Sequoia
Impact: An app may be able to trick a user into copying sensitive data to the pasteboard
Description: A configuration issue was addressed with additional restrictions.
CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH)
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24266: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2025-24265: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24157: an anonymous researcher
-

@ b9f4c34d:7d1a0e31
2025-04-02 15:02:59
<p> testssss </p>
-

@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20
<h2> Test Video Document </h2>
-

@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02
<h1> Testy McTestenface </h1>
<p> It's been so long, html </p>
-

@ 8d34bd24:414be32b
2025-04-02 14:13:03
I was reading this passage last night:
> …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine}
Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself.
This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation.
> And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28)
When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect:
> And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine}
When one particular man said that he would follow Jesus anywhere, Jesus responded this way.
> As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine}
Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort.
> “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine}
Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect.
> “**For my thoughts are not your thoughts,\
> neither are your ways my ways**,”\
> declares the Lord.
>
> “As the heavens are higher than the earth,\
> so are **my ways higher than your ways**\
> and my thoughts than your thoughts.
>
> As the rain and the snow\
> come down from heaven,\
> and do not return to it\
> without watering the earth\
> and making it bud and flourish,\
> so that it yields seed for the sower and bread for the eater,\
> so is **my word that goes out from my mouth:\
> It will not return to me empty,\
> but will accomplish what I desire\
> and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine}
God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us.
> Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine}
In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word.
> They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine}
Peter specifically warns believers to expect trials and hardship.
> Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And,
>
> “If it is hard for the righteous to be saved,\
> what will become of the ungodly and the sinner?”
>
> So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine}
Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship.
> …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine}
No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good.
> Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written,
>
> “For Your sake we are being put to death all day long;\
> We were considered as sheep to be slaughtered.”
> ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine}
I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be.
First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard.
Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion.
In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before.
When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good.
We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness.
> Oh, the depth of the riches of the wisdom and knowledge of God!\
> How unsearchable his judgments,\
> and his paths beyond tracing out!\
> “Who has known the mind of the Lord?\
> Or who has been his counselor?”\
> “Who has ever given to God,\
> that God should repay them?”\
> For from him and through him and for him are all things.\
> To him be the glory forever! Amen. (Romans 11:33-36)
Trust Jesus
-

@ 06639a38:655f8f71
2025-04-02 13:47:57
You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github.
Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits.
Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19)
### **TLV's**
Things were getting more complicated with the other prefixes / identifiers defined in NIP-19:
* `nevent`
* `naddr`
* `nprofile`
This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's.
_When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._
_For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._
These possible standardized `TLV` types are:
* `0`_:_ `special`
* _depends on the bech32 prefix:_
* _for_ `nprofile` _it will be the 32 bytes of the profile public key_
* _for_ `nevent` _it will be the 32 bytes of the event id_
* _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._
* `1`_:_ `relay`
* _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_
* _this may be included multiple times_
* `2`_:_ `author`
* _for_ `naddr`_, the 32 bytes of the pubkey of the event_
* _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_
* `3`_:_ `kind`
* _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_
* _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_
These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters.
Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code):
* [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74)
* [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19)
### **So what's next?**
* NIP-19 code housekeeping + refactoring
* Prepare a new release with NIP-19 integration
* Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev)
-

@ 7bdef7be:784a5805
2025-04-02 12:37:35
The following script try, using [nak](https://github.com/fiatjaf/nak), to find out the last ten people who have followed a `target_pubkey`, sorted by the most recent. It's possibile to shorten `search_timerange` to speed up the search.
```
#!/usr/bin/env fish
# Target pubkey we're looking for in the tags
set target_pubkey "6e468422dfb74a5738702a8823b9b28168abab8655faacb6853cd0ee15deee93"
set current_time (date +%s)
set search_timerange (math $current_time - 600) # 24 hours = 86400 seconds
set pubkeys (nak req --kind 3 -s $search_timerange wss://relay.damus.io/ wss://nos.lol/ 2>/dev/null | \
jq -r --arg target "$target_pubkey" '
select(. != null and type == "object" and has("tags")) |
select(.tags[] | select(.[0] == "p" and .[1] == $target)) |
.pubkey
' | sort -u)
if test -z "$pubkeys"
exit 1
end
set all_events ""
set extended_search_timerange (math $current_time - 31536000) # One year
for pubkey in $pubkeys
echo "Checking $pubkey"
set events (nak req --author $pubkey -l 5 -k 3 -s $extended_search_timerange wss://relay.damus.io wss://nos.lol 2>/dev/null | \
jq -c --arg target "$target_pubkey" '
select(. != null and type == "object" and has("tags")) |
select(.tags[][] == $target)
' 2>/dev/null)
set count (echo "$events" | jq -s 'length')
if test "$count" -eq 1
set all_events $all_events $events
end
end
if test -n "$all_events"
echo -e "Last people following $target_pubkey:"
echo -e ""
set sorted_events (printf "%s\n" $all_events | jq -r -s '
unique_by(.id) |
sort_by(-.created_at) |
.[] | @json
')
for event in $sorted_events
set npub (echo $event | jq -r '.pubkey' | nak encode npub)
set created_at (echo $event | jq -r '.created_at')
if test (uname) = "Darwin"
set follow_date (date -r "$created_at" "+%Y-%m-%d %H:%M")
else
set follow_date (date -d @"$created_at" "+%Y-%m-%d %H:%M")
end
echo "$follow_date - $npub"
end
end
```
-

@ fd06f542:8d6d54cd
2025-04-02 12:34:07
- [首页](/readme.md)
- [国内开发者](/01.md)
-

@ 7bdef7be:784a5805
2025-04-02 12:12:12
We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs.
## The problem
Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so **everyone can actually snoop what we are interested in**, and what is supposable that we read daily.
## The solution
Nostr has a simple solution for this necessity: **encrypted lists**.
Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, **we can hide the lists' content from others**.
The implications are obvious: we can not only have a more organized way to browse content, but it is also **really private one**.
One might wonder what use can really be made of private lists; here are some examples:
* Browse “can't miss” content from users I consider a priority;
* Supervise competitors or adversarial parts;
* Monitor sensible topics (tags);
* Following someone without being publicly associated with them, as this may be undesirable;
The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of **how many bots scan our actions to profile us**.
## The current state
Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity.
Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an **easier option** to start offering private lists: give the user **the possibility to simply mark them as local-only**, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment.
To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage **both encrypted and local-only lists**.
Beg your Nostr client to implement private lists!
-

@ 04cb16e4:2ec3e5d5
2025-04-02 10:51:31
Wenn irgendein weltpolitisches Thema auf den Tisch kommt, wird zumeist erst einmal gefragt, ob du dafür oder dagegen bist und auf welcher Seite du dich befindest. Das macht es einfacher, dich als Freund oder Feind einzusortieren. So wird das Leben übersichtlicher und man muss nicht in die Tiefe gehen und sich mit lästigen Details auseinandersetzen. Man muss auch nicht verreisen um sich ein Bild zu machen. Dafür gibt es ja die Tagesschau. Klassisches Beispiel: Ich war vor Kurzem mit einigen Freunden essen. Einer berichtete entsetzt: „Der Putin hat die Heimatstadt von Selenski angegriffen!“
 Ich versuchte mir das bildlich vorzustellen und kam zu dem Schluss, das „der Putin“ wahrscheinlich Verstärkung dabei hatte. Und ausgerechnet nachdem Trump und dessen Flügelmann Vance den armen Wolodymyr rund gemacht hatten, greift der böse Imperator dessen Heimatstadt an. Das ist fies! Das macht „der Putin“ wahrscheinlich immer so, wenn er jemandem eins auswischen will. Die Heimatstadt angreifen! Ganz gleich, ob es strategisch gerade Sinn macht oder nicht. "Der Putin" ist halt ein Teufel.
[Telegramkanal RBM](https://t.me/radio_berliner_morgenroete_de)
[Radio Berliner Morgenröte auf X](https://x.com/RBM_Schindler)
Ich denke viele gucken einfach zu viele qualitativ minderwertige Spielfilme und können Fiktion und Realität nicht mehr voneinander unterscheiden. Möglicherweise meinen sie auch, weil sie die Handlung eines Kriegsfilmes gerafft haben, verstehen sie einen Krieg.
<https://www.eisbrenner.de/produkt-kategorie/buch/>
<https://befreiung.org/>
Mein Gesprächspartner Tino Eisbrenner hat keine Sightseeing Tour durch Moskau gemacht, sondern ist in Land und Leute regelrecht eingetaucht. Außerdem kommt seine Schwiegermutter aus Russland. Da ist man dem ganzen auch menschlich viel näher und bekommt man ganz andere Einblicke als die, die einem von der Tagesschau gewährt werden. Tino ist als Friedensmusiker viel im Osten unterwegs, unter anderem auch in Georgien, Weißrussland und auf der Krim. Er spricht mit Politikern, Künstlern, Journalisten, Taxifahrern und Dissidenten. Und viele fragen ihn: „Was ist eigentlich mit den Deutschen los?“ Gute Frage! Was ist eigentlich mit uns los? Wir senden unsere Volksvertreter in die Welt hinaus, damit sie Staatsoberhäuptern aus Ländern - die um ein Vielfaches umfangreicher an Fläche und Einwohnerzahl sind und eine komplett andere Kulturgeschichte haben - damit sie denen erklären können wie man seinen Job macht. Wahrscheinlich in dem irrwitzigen Glauben, dass sie selbst ihren Job tadellos und vorbildlich ausführen.
**Spenden nehmen wir entweder mit dem Paypal Button am Ende** **[unserer Webseite](https://radio-berliner-morgenroete.de/)** **<https://radio-berliner-morgenroete.de/>** **oder per Überweisung aufs Bankkonto: DE93 1001 1001 2624 3740 74 entgegen.**
Wir sind aber nicht nur verantwortlich für unsere politische Führung, sondern auch für unseren Umgang miteinander. Denn im „Großen“ gilt dasselbe wie im „Kleinen“! Man sollte erst mal bei sich selbst schauen wo es hakt und dann miteinander ins Gespräch gehen. Der Mangel an Realitätssinn und Konfliktfähigkeit zieht sich durch alle Schichten unserer Bevölkerung. Deswegen sagt Radio Berliner Morgenröte: „Wenn ihr Frieden wollt, fangt in Deutschland an und wenn ihr euch eine Meinung über Russland oder China bilden wollt, dann fahrt einfach mal dorthin und redet mit den Leuten, So wie Tino. Mir hat es riesig Spaß gemacht, ihm zuzuhören.
Weiterer Buchtipp – [Ausgegendert](https://www.masselverlag.de/v/yHj2uBdfbu/)
<https://mcdn.podbean.com/mf/web/e5qbg23gz6mru9zz/Tino_Eisbrenner9tbpx.mp3>
-

@ d04ecf33:1d62aa90
2025-04-02 09:48:16
## Physical prototyping
3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes.
Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations.
## Prototypers of Ideas
Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop.
However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car.
From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase.
And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc.
So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better.
## Economic Impact
3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare.
Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away.
## Progress
LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators.
If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today.
If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences.
Keep printing ideas and execute on them!
Learn and repeat. The path to success.
#llm #ai #agi #3dp #programming
-

@ 7d33ba57:1b82db35
2025-04-02 08:15:08
Supetar is the main town and ferry port on Brač Island, located just across the sea from Split. It’s a charming coastal town with historic streets, beautiful beaches, and a relaxed island vibe. As the main entry point to Brač, it’s the perfect base for exploring the island’s stunning beaches, olive groves, and cultural landmarks.

## **🏛️ Top Things to See & Do in Supetar**
### **1️⃣ Explore the Supetar Old Town 🏡**
- Stroll through **narrow, stone-paved alleys**, lined with **historic buildings and seaside cafés**.
- Visit **St. Peter’s Church & Mausoleum**, featuring intricate stone carvings.
- Admire the **harbor filled with fishing boats**, offering postcard-worthy views.
### **2️⃣ Relax on Supetar’s Beaches 🏖️**
- **Banj Beach** – A **family-friendly beach** with crystal-clear water & soft pebbles.
- **Acapulco Beach** – A more secluded, **rocky beach with turquoise waters**.
- **Vela Luka Bay** – A beautiful bay **surrounded by pine forests**, perfect for relaxation.
### **3️⃣ Visit the Olive Oil Museum in Škrip 🫒**
- **Just 15 minutes from Supetar**, this museum showcases **Brač’s olive oil heritage**.
- Try traditional **Dalmatian olive oil tastings** & local island delicacies.

### **4️⃣ Take a Boat Trip to the Famous Zlatni Rat Beach ⛵**
- One of **Croatia’s most iconic beaches**, known for its **shifting horn-shaped coastline**.
- Located in **Bol**, just a short boat or car ride away from Supetar.
### **5️⃣ Hike or Drive to Vidova Gora 🌄**
- The **highest peak on the Adriatic islands (778m)**, offering **breathtaking views** over Brač, Hvar, and beyond.
- Accessible by **hiking (moderate difficulty) or driving**.

### **6️⃣ Try Dalmatian Cuisine 🍽️**
- **Vitalac** – A unique Brač specialty, made from lamb offal and cooked over an open fire.
- **Pašticada** – A slow-cooked beef dish, traditionally served with gnocchi.
- **Homemade Brač cheese & wine** – Try local goat cheese paired with **Plavac Mali wine**.

## **🚗 How to Get to Supetar**
⛴️ **By Ferry (from Split):**
- The **Split-Supetar ferry** is the **main connection** (50 min ride).
- Ferries run **frequently** (especially in summer).
🚘 **By Car:**
- **Supetar is the best entry point for road trips across Brač**.
- Car rentals are available in town or at the ferry port.

## **💡 Tips for Visiting Supetar**
✅ **Best time to visit?** **May–September** for warm weather & clear seas ☀️
✅ **Stay at least a night** – Supetar has a lovely evening atmosphere 🌙
✅ **Rent a scooter or car** to explore Brač’s hidden beaches & inland villages 🏍️
✅ **Try local wines & olive oils** – Brač is famous for both 🍷🫒
✅ **Visit early in the morning** for a peaceful experience before ferries get busy ⏳

 @ 2749c032:ef202a37
2025-04-04 08:07:16 send 1k satoshi and send me your email for delivery {please allow delivery to take up to 24hrs max. i'm only 1 man and stay busy offline and i do enjoy my sleep} originally posted at https://stacker.news/items/934145
@ 2749c032:ef202a37
2025-04-04 08:07:16 send 1k satoshi and send me your email for delivery {please allow delivery to take up to 24hrs max. i'm only 1 man and stay busy offline and i do enjoy my sleep} originally posted at https://stacker.news/items/934145 @ 266815e0:6cd408a5
2025-04-04 07:54:02This should be published to nostr using nostr-connect account
@ 266815e0:6cd408a5
2025-04-04 07:54:02This should be published to nostr using nostr-connect account @ 2749c032:ef202a37
2025-04-04 07:51:18🇨🇦🌎🇺🇸 **ESCROW AVAILABLE ** 💳💰🏧🔑💻💵📬 DWVendor DM for full product list or inquiries https://t.me/whiteyfrauds https://x.com/whiteyshub https://snort.social?ref=undefined originally posted at https://stacker.news/items/924998
@ 2749c032:ef202a37
2025-04-04 07:51:18🇨🇦🌎🇺🇸 **ESCROW AVAILABLE ** 💳💰🏧🔑💻💵📬 DWVendor DM for full product list or inquiries https://t.me/whiteyfrauds https://x.com/whiteyshub https://snort.social?ref=undefined originally posted at https://stacker.news/items/924998 @ 3104fbbf:ac623068
2025-04-04 06:58:30 ## **Introduction** If you have a functioning brain, it’s impossible to fully stand for any politician or align completely with any political party. The solutions we need are not found in the broken systems of power but in individual actions and local initiatives. Voting for someone may be your choice, but relying solely on elections every few years as a form of political activism is a losing strategy. People around the world have fallen into the trap of thinking that casting a ballot once every four years is enough, only to return to complacency as conditions worsen. Voting for the "lesser of two evils" has been the norm for decades, yet expecting different results from the same flawed system is naive at best. The truth is, governments are too corrupt to save us. In times of crisis, they won’t come to your aid—instead, they will tighten their grip, imposing more surveillance, control, and wealth extraction to benefit the oligarch class. To break free from this cycle, we must first protect ourselves individually—financially, geographically, and digitally—alongside our families. Then, we must organize and build resilient local communities. These are the only ways forward. History has shown us time and again that the masses are easily deceived by the political circus, falling for the illusion of a "savior" who will fix everything. But whether right, center, or left, the story remains the same: corruption, lies, and broken promises. If you possess a critical and investigative mind, you know better than to place your trust in politicians, parties, or self-proclaimed heroes. The real solution lies in free and sovereign individuals who reject the herd mentality and take responsibility for their own lives. From the beginning of time, true progress has come from individuals who think for themselves and act independently. The nauseating web of politicians, billionaires, and oligarchs fighting for power and resources has never been—and will never be—the answer to our problems. In a world increasingly dominated by corrupted governments, NGOs, and elites, ordinary people must take proactive steps to protect themselves and their families. --- ## **1. Financial Protection: Reclaiming Sovereignty Through Bitcoin** Governments and central banks have long manipulated fiat currencies, eroding wealth through inflation and bailouts that transfer resources to the oligarch class. Bitcoin, as a decentralized, censorship-resistant, and finite currency, offers a way out. Here’s what individuals can do: - **Adopt Bitcoin as a Savings Tool**: Shift a portion of your savings into Bitcoin to protect against inflation and currency devaluation. Bitcoin’s fixed supply (21 million coins) ensures it cannot be debased like fiat money. - **Learn Self-Custody**: Store your Bitcoin in a hardware wallet or use open-source software wallets. Avoid centralized exchanges, which are vulnerable to government seizure or collapse. - **Diversify Geographically:** Hold assets in multiple jurisdictions to reduce the risk of confiscation or capital controls. Consider offshore accounts or trusts if feasible. - **Barter and Local Economies**: In times of crisis, local barter systems and community currencies can bypass failing national systems. Bitcoin can serve as a global medium of exchange in such scenarios. --- ## 2. Geographical Flexibility: Reducing Dependence on Oppressive Systems Authoritarian regimes thrive on controlling populations within fixed borders. By increasing geographical flexibility, individuals can reduce their vulnerability: - **Obtain Second Passports or Residencies**: Invest in citizenship-by-investment programs or residency permits in countries with greater freedoms and lower surveillance. - **Relocate to Freer Jurisdictions**: Research and consider moving to regions with stronger property rights, lower taxes, and less government overreach. - **Decentralize Your Life**: Avoid keeping all your assets, family, or business operations in one location. Spread them across multiple regions to mitigate risks. --- ## 3. Digital Privacy: Fighting Surveillance with Advanced Tools The rise of mass surveillance and data harvesting by governments and corporations threatens individual freedom. Here’s how to protect yourself: - **Use Encryption**: Encrypt all communications using tools like Signal or ProtonMail. Ensure your devices are secured with strong passwords and biometric locks. - **Adopt Privacy-Focused Technologies**: Use Tor for anonymous browsing, VPNs to mask your IP address, and open-source operating systems like Linux to avoid backdoors. - **Reject Surveillance Tech**: Avoid smart devices that spy on you (e.g., Alexa, Google Home). Opt for decentralized alternatives like Mastodon instead of Twitter, or PeerTube instead of YouTube. - **Educate Yourself on Digital Privacy**: Learn about tools and practices that enhance your online privacy and security. --- ## 4. Building Resilient Local Communities: The Foundation of a Free Future While individual actions are crucial, collective resilience is equally important. Governments are too corrupt to save populations in times of crisis—history shows they will instead impose more control and transfer wealth to the elite. To counter this, communities must organize locally: - **Form Mutual Aid Networks**: Create local groups that share resources, skills, and knowledge. These networks can provide food, medical supplies, and security during crises. - **Promote Local Economies**: Support local businesses, farmers, and artisans. Use local currencies or barter systems to reduce dependence on centralized financial systems. - **Develop Off-Grid Infrastructure**: Invest in renewable energy, water filtration, and food production to ensure self-sufficiency. Community gardens, solar panels, and rainwater harvesting are excellent starting points. - **Educate and Empower**: Host workshops on financial literacy, digital privacy, and sustainable living. Knowledge is the most powerful tool against authoritarianism. --- ## 5. The Bigger Picture: Rejecting the Illusion of Saviors The deep corruption within governments, NGOs, and the billionaire class is evident. These entities will never act in the interest of ordinary people. Instead, they will exploit crises to expand surveillance, control, and wealth extraction. The idea of a political “savior” is a dangerous illusion. True freedom comes from individuals taking responsibility for their own lives and working together to build decentralized, resilient systems. --- ## Conclusion: A Call to Action The path to a genuinely free humanity begins with individual action. By adopting Bitcoin, securing digital privacy, increasing geographical flexibility, and building resilient local communities, ordinary people can protect themselves against authoritarianism. Governments will not save us—they are the problem. It is up to us to create a better future, free from the control of corrupt elites. - The tools for liberation already exist. - The question is: will we use them? For those interested, I share ideas and solutions in my book « THE GATEWAY TO FREEDOM » https://blisshodlenglish.substack.com/p/the-gateway-to-freedom ⚡ **The time to act is now. Freedom is not given—it is taken.** ⚡ ###### If you enjoyed this article, consider supporting it with a Zap! --- My Substack ENGLISH = https://blisshodlenglish.substack.com/ My substack FRENCH = https://blisshodl.substack.com/ --- Get my Book « THE GATEWAY TO FREEDOM » here 🙏 => https://coinos.io/blisshodl --- ---
@ 3104fbbf:ac623068
2025-04-04 06:58:30 ## **Introduction** If you have a functioning brain, it’s impossible to fully stand for any politician or align completely with any political party. The solutions we need are not found in the broken systems of power but in individual actions and local initiatives. Voting for someone may be your choice, but relying solely on elections every few years as a form of political activism is a losing strategy. People around the world have fallen into the trap of thinking that casting a ballot once every four years is enough, only to return to complacency as conditions worsen. Voting for the "lesser of two evils" has been the norm for decades, yet expecting different results from the same flawed system is naive at best. The truth is, governments are too corrupt to save us. In times of crisis, they won’t come to your aid—instead, they will tighten their grip, imposing more surveillance, control, and wealth extraction to benefit the oligarch class. To break free from this cycle, we must first protect ourselves individually—financially, geographically, and digitally—alongside our families. Then, we must organize and build resilient local communities. These are the only ways forward. History has shown us time and again that the masses are easily deceived by the political circus, falling for the illusion of a "savior" who will fix everything. But whether right, center, or left, the story remains the same: corruption, lies, and broken promises. If you possess a critical and investigative mind, you know better than to place your trust in politicians, parties, or self-proclaimed heroes. The real solution lies in free and sovereign individuals who reject the herd mentality and take responsibility for their own lives. From the beginning of time, true progress has come from individuals who think for themselves and act independently. The nauseating web of politicians, billionaires, and oligarchs fighting for power and resources has never been—and will never be—the answer to our problems. In a world increasingly dominated by corrupted governments, NGOs, and elites, ordinary people must take proactive steps to protect themselves and their families. --- ## **1. Financial Protection: Reclaiming Sovereignty Through Bitcoin** Governments and central banks have long manipulated fiat currencies, eroding wealth through inflation and bailouts that transfer resources to the oligarch class. Bitcoin, as a decentralized, censorship-resistant, and finite currency, offers a way out. Here’s what individuals can do: - **Adopt Bitcoin as a Savings Tool**: Shift a portion of your savings into Bitcoin to protect against inflation and currency devaluation. Bitcoin’s fixed supply (21 million coins) ensures it cannot be debased like fiat money. - **Learn Self-Custody**: Store your Bitcoin in a hardware wallet or use open-source software wallets. Avoid centralized exchanges, which are vulnerable to government seizure or collapse. - **Diversify Geographically:** Hold assets in multiple jurisdictions to reduce the risk of confiscation or capital controls. Consider offshore accounts or trusts if feasible. - **Barter and Local Economies**: In times of crisis, local barter systems and community currencies can bypass failing national systems. Bitcoin can serve as a global medium of exchange in such scenarios. --- ## 2. Geographical Flexibility: Reducing Dependence on Oppressive Systems Authoritarian regimes thrive on controlling populations within fixed borders. By increasing geographical flexibility, individuals can reduce their vulnerability: - **Obtain Second Passports or Residencies**: Invest in citizenship-by-investment programs or residency permits in countries with greater freedoms and lower surveillance. - **Relocate to Freer Jurisdictions**: Research and consider moving to regions with stronger property rights, lower taxes, and less government overreach. - **Decentralize Your Life**: Avoid keeping all your assets, family, or business operations in one location. Spread them across multiple regions to mitigate risks. --- ## 3. Digital Privacy: Fighting Surveillance with Advanced Tools The rise of mass surveillance and data harvesting by governments and corporations threatens individual freedom. Here’s how to protect yourself: - **Use Encryption**: Encrypt all communications using tools like Signal or ProtonMail. Ensure your devices are secured with strong passwords and biometric locks. - **Adopt Privacy-Focused Technologies**: Use Tor for anonymous browsing, VPNs to mask your IP address, and open-source operating systems like Linux to avoid backdoors. - **Reject Surveillance Tech**: Avoid smart devices that spy on you (e.g., Alexa, Google Home). Opt for decentralized alternatives like Mastodon instead of Twitter, or PeerTube instead of YouTube. - **Educate Yourself on Digital Privacy**: Learn about tools and practices that enhance your online privacy and security. --- ## 4. Building Resilient Local Communities: The Foundation of a Free Future While individual actions are crucial, collective resilience is equally important. Governments are too corrupt to save populations in times of crisis—history shows they will instead impose more control and transfer wealth to the elite. To counter this, communities must organize locally: - **Form Mutual Aid Networks**: Create local groups that share resources, skills, and knowledge. These networks can provide food, medical supplies, and security during crises. - **Promote Local Economies**: Support local businesses, farmers, and artisans. Use local currencies or barter systems to reduce dependence on centralized financial systems. - **Develop Off-Grid Infrastructure**: Invest in renewable energy, water filtration, and food production to ensure self-sufficiency. Community gardens, solar panels, and rainwater harvesting are excellent starting points. - **Educate and Empower**: Host workshops on financial literacy, digital privacy, and sustainable living. Knowledge is the most powerful tool against authoritarianism. --- ## 5. The Bigger Picture: Rejecting the Illusion of Saviors The deep corruption within governments, NGOs, and the billionaire class is evident. These entities will never act in the interest of ordinary people. Instead, they will exploit crises to expand surveillance, control, and wealth extraction. The idea of a political “savior” is a dangerous illusion. True freedom comes from individuals taking responsibility for their own lives and working together to build decentralized, resilient systems. --- ## Conclusion: A Call to Action The path to a genuinely free humanity begins with individual action. By adopting Bitcoin, securing digital privacy, increasing geographical flexibility, and building resilient local communities, ordinary people can protect themselves against authoritarianism. Governments will not save us—they are the problem. It is up to us to create a better future, free from the control of corrupt elites. - The tools for liberation already exist. - The question is: will we use them? For those interested, I share ideas and solutions in my book « THE GATEWAY TO FREEDOM » https://blisshodlenglish.substack.com/p/the-gateway-to-freedom ⚡ **The time to act is now. Freedom is not given—it is taken.** ⚡ ###### If you enjoyed this article, consider supporting it with a Zap! --- My Substack ENGLISH = https://blisshodlenglish.substack.com/ My substack FRENCH = https://blisshodl.substack.com/ --- Get my Book « THE GATEWAY TO FREEDOM » here 🙏 => https://coinos.io/blisshodl --- --- @ bf95e1a4:ebdcc848
2025-04-04 06:11:18This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our[ Geyser page](https://geyser.fund/project/infinity)! ## The Gullible Collective We humans are biased by nature. Everything we think we know is distorted in one way or another by our cognitive shortcomings. The human brain has been forced to evolve and adapt to whatever environment it found itself in over millennia. Having a brain that is capable of setting aside personal aims for the sake of the collective has proven to be advantageous for the evolution of our species as a whole. The same is true for every other social life form. However, letting these parts of our brains guide our political judgment can lead to disastrous results in the long run — not because of bad intentions but because of the simple fact that a few individuals will always thrive by playing every political system for personal gain. From an evolutionary perspective, an army of ay-sayers and martyrs, regardless of whether we’re talking about an army of humans or an army of ants or bacteria, has an advantage over a less disciplined one. From an individual's evolutionary perspective though, it is better to *appear* like you’re a martyr but to run and hide when the actual battle happens. This at least partly explains the high percentage of sociopaths in leadership positions all over the world. If you can appear to act for the good of the collective but dupe your way into more and more power behind people’s backs, you’re more likely to succeed than someone playing a fair game. The story of banking and fiat currency is a story about collective madness. Historically, rulers have tricked people into killing each other through the promise of an after-life. Through central banking, the rulers of the world wars could trick people into building armies for them by printing more money. This is seldom mentioned in history classes because it still goes on today on a massive scale. Inflation might no longer be paying tank factory workers, but it is the main mechanism that funnels wealth into the pockets of the super-rich and away from everyone else. Inflation is the mechanism that hinders us from transporting the value of our labor through time. It makes us avoid real long-term thinking. We hardly ever consider this a problem because none of us has ever experienced an alternative to it. Money is still vastly misunderstood by the lion's share of the world’s population. In most parts of the world, banks do something called fractional reserve lending. This means that they lend out money that they don't have — conjuring up new money out of thin air and handing it out to their customers as loans. Loans that have to be paid back with interest. Interest that can’t be paid back with thin air but has to be paid with so-called real money. Real money, of which there isn’t enough around to pay back all the loans, so that a constant need for new credit becomes a crucial part of the entire system. Not to mention central banks, which do the same and worse for governments. We’re so used to it by now that every country is expected to have a national debt. All but a handful of ridiculously rich ones do. National debts are also loans that have to be paid back with interest backed by nothing. Think about that. Your taxes are paying someone else's interest. Your tax money is not paying for your grandmother's bypass operation, it is paying interest to a central bank. When the ideas of the catholic church ruled Europe, people who didn’t believe in God were few and very seldomly outspoken. They had good reason for this since belief in God was virtually mandatory throughout society. Ever since 1971, when famously dishonest American president Richard Nixon cut the last string that tied the US Dollar to gold, our conception of what the world economy is and ought to be has been skewed by an utterly corrupt system. We’re led to believe that we’re all supposed to work longer and longer days in order to spend more and more money and bury ourselves in more and more debt to keep the machine running. We’re duped into thinking that buying a new car every other year is somehow good for the environment and that bringing a cotton bag to the grocery store will somehow save the planet. Stores manipulate us all the time through advertising and product placement, but we’re led to believe that if we can be “climate-smart,” we’re behaving responsibly. Somehow, our gross domestic product is supposed to increase indefinitely while politicians will save us from ourselves through carbon taxes. Fortunately for us, and unfortunately for them, there now exists a way for unbelievers of this narrative to opt out. Life finds a way, as Jeff Goldblum once so famously put it. Collectivism has ruined many societies. Those of us fortunate enough to live in liberal democracies tend to forget that even democracy is an involuntary system. It’s often referred to as the “worst form of government except all others that have been tried,” but the system itself is very rarely criticized. We’re so used to being governed that not having a leader seems preposterous to most of us. Still, we pay our taxes, and an enormous cut of the fruit of our labor goes to a third party via inflation and the taxation of every good and service imaginable. Institutions, once in place, tend to always favor their own survival just as much as any other living thing does. People employed in the public sector are unlikely to vote against policies that threaten their livelihood. This is a bigger problem than we realize because it’s subtle and takes a long time, but every democracy is headed in the same direction. A bigger state, a more complicated system, and fewer individual freedoms. Long term, it seems that all of our systems tend to favor those who know how to play that system and not those who contribute the most value to their fellow man. Proponents of socialist policies often claim that failed socialist states “weren’t really socialist” or that “that wasn’t really socialism.” What most people fail to realize is that we’ve never tried real *capitalism* since we’ve always used more or less inflationary currencies. This might very well be the most skewed narrative of our era. We’re all experiencing real, albeit disguised, socialism every single day. True free market capitalism is what we haven’t experienced yet, and it might turn out to be a very different thing than what we’re told to believe that it is by almost all mainstream media. The validity of the classic right-left scale describing political viewpoints has been debated a lot lately, and alternative scales, like GAL-TAN, the one with an additional Y-axis describing more or less authoritarian tendencies, are popping up in various contexts around the web. After the birth of Bitcoin, there’s a new way to see this. Imagine an origo, a zero point, and a vector pointing to the left of that. *All* politics are arguably on the left because *all* policies need to be funded by taxes, and taxation can be viewed as theft. Taxation can be viewed as theft because, at its core, it’s involuntary. If a person refuses to pay his taxes, there is a threat of violence lurking in the background. Not to mention inflation, which Milton Friedman so elegantly described as “taxation without legislation.” What you do with the portion of your wealth that you have in Bitcoin is another matter altogether. If you take sufficient precautionary privacy measures and you know what you’re doing, your business in Bitcoin is beyond politics altogether. With the introduction of the Lightning Network and other privacy-improving features, it is now impossible for any third party to confiscate your money or even know that you have it, for that matter. This changes the political landscape of every nation on Earth. Bitcoin is much less confiscatable than gold and other scarce assets, which makes it a much better tool for hedging against nation-states. In this sense, Bitcoin obsoletes borders. You can cross any border on Earth with any amount of Bitcoin *in your head*. Think about that! Your Bitcoin exists in every country simultaneously. Any imposed limit on how much money you can carry from one nation to the other is now made obsolete by beautiful mathematics. Bitcoin is sometimes referred to as a “virtual currency.” This is a very inaccurate description. Bitcoin is just mathematics, and mathematics is just about the most real thing there is. There’s nothing virtual about it. Counterintuitive to some, but real nonetheless. The complexity of human societal hierarchies and power structures is described perfectly in a classic children's book, *The Emperor’s New Clothes*, by Hans Christian Andersen. See the world as the kid who points out that the king is naked in the tale, and everything starts to make sense. Everything in human society is man-made. Nations, leaders, laws, political systems. They’re all castles in the air with nothing but a lurking threat of violence to back them up. Bitcoin is a different beast altogether. It enables every individual to verify the validity of the system at all times. If you really think about it, morality is easy. Don’t hurt other people, and don’t steal other people’s stuff. That’s the basic premise. Humans have but two ways of resolving conflict, conversation and violence, and in this sense, to hurt someone can only mean physical violence. This is why free speech is so important and why you should defend people’s right to speak their minds above everything else. It’s not about being able to express yourself. It’s about your right to hear every side of every argument and thus not have to resort to violence should a conflict of interests occur. You can’t limit free speech with just more speech — there’s always a threat of violence behind the limitations. Code, which both Bitcoin and the Internet are entirely made up of, *is speech*. Any limitations or regulations that your government implements in regard to Bitcoin are not only a display of Bitcoin’s censorship resistance but also a test of your government's stance on freedom of expression. A restriction on Bitcoin use is a restriction on free speech. Remember, the only alternative to speech that anyone has is violence. Code is a language, mathematics is a language, and money is a linguistic tool. A linguistic tool we use as a means of expressing value to each other and as a way to transport value through space and time. Any restrictions or regulations regarding how you can express value, for example, making it impossible to buy Bitcoin with your credit card, prove that the money you have in your bank account is not really yours. When people realize this, the demand for Bitcoin goes *up*, not down. If you know what you're doing, there’s no need to fear the regulators. They, on the other hand, have good reason to fear an invention that shamelessly breaks their spell. ### **About the Bitcoin Infinity Academy** The Bitcoin Infinity Academy is an educational project built around [Knut Svanholm](http://primal.net/knut)’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a [video](https://www.youtube.com/@BitcoinInfinityShow) in which Knut and [Luke de Wolf](http://primal.net/luke) discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our [Geyser](https://geyser.fund/project/infinity) page. Signed books, monthly calls, and lots of other benefits are also available.
@ bf95e1a4:ebdcc848
2025-04-04 06:11:18This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our[ Geyser page](https://geyser.fund/project/infinity)! ## The Gullible Collective We humans are biased by nature. Everything we think we know is distorted in one way or another by our cognitive shortcomings. The human brain has been forced to evolve and adapt to whatever environment it found itself in over millennia. Having a brain that is capable of setting aside personal aims for the sake of the collective has proven to be advantageous for the evolution of our species as a whole. The same is true for every other social life form. However, letting these parts of our brains guide our political judgment can lead to disastrous results in the long run — not because of bad intentions but because of the simple fact that a few individuals will always thrive by playing every political system for personal gain. From an evolutionary perspective, an army of ay-sayers and martyrs, regardless of whether we’re talking about an army of humans or an army of ants or bacteria, has an advantage over a less disciplined one. From an individual's evolutionary perspective though, it is better to *appear* like you’re a martyr but to run and hide when the actual battle happens. This at least partly explains the high percentage of sociopaths in leadership positions all over the world. If you can appear to act for the good of the collective but dupe your way into more and more power behind people’s backs, you’re more likely to succeed than someone playing a fair game. The story of banking and fiat currency is a story about collective madness. Historically, rulers have tricked people into killing each other through the promise of an after-life. Through central banking, the rulers of the world wars could trick people into building armies for them by printing more money. This is seldom mentioned in history classes because it still goes on today on a massive scale. Inflation might no longer be paying tank factory workers, but it is the main mechanism that funnels wealth into the pockets of the super-rich and away from everyone else. Inflation is the mechanism that hinders us from transporting the value of our labor through time. It makes us avoid real long-term thinking. We hardly ever consider this a problem because none of us has ever experienced an alternative to it. Money is still vastly misunderstood by the lion's share of the world’s population. In most parts of the world, banks do something called fractional reserve lending. This means that they lend out money that they don't have — conjuring up new money out of thin air and handing it out to their customers as loans. Loans that have to be paid back with interest. Interest that can’t be paid back with thin air but has to be paid with so-called real money. Real money, of which there isn’t enough around to pay back all the loans, so that a constant need for new credit becomes a crucial part of the entire system. Not to mention central banks, which do the same and worse for governments. We’re so used to it by now that every country is expected to have a national debt. All but a handful of ridiculously rich ones do. National debts are also loans that have to be paid back with interest backed by nothing. Think about that. Your taxes are paying someone else's interest. Your tax money is not paying for your grandmother's bypass operation, it is paying interest to a central bank. When the ideas of the catholic church ruled Europe, people who didn’t believe in God were few and very seldomly outspoken. They had good reason for this since belief in God was virtually mandatory throughout society. Ever since 1971, when famously dishonest American president Richard Nixon cut the last string that tied the US Dollar to gold, our conception of what the world economy is and ought to be has been skewed by an utterly corrupt system. We’re led to believe that we’re all supposed to work longer and longer days in order to spend more and more money and bury ourselves in more and more debt to keep the machine running. We’re duped into thinking that buying a new car every other year is somehow good for the environment and that bringing a cotton bag to the grocery store will somehow save the planet. Stores manipulate us all the time through advertising and product placement, but we’re led to believe that if we can be “climate-smart,” we’re behaving responsibly. Somehow, our gross domestic product is supposed to increase indefinitely while politicians will save us from ourselves through carbon taxes. Fortunately for us, and unfortunately for them, there now exists a way for unbelievers of this narrative to opt out. Life finds a way, as Jeff Goldblum once so famously put it. Collectivism has ruined many societies. Those of us fortunate enough to live in liberal democracies tend to forget that even democracy is an involuntary system. It’s often referred to as the “worst form of government except all others that have been tried,” but the system itself is very rarely criticized. We’re so used to being governed that not having a leader seems preposterous to most of us. Still, we pay our taxes, and an enormous cut of the fruit of our labor goes to a third party via inflation and the taxation of every good and service imaginable. Institutions, once in place, tend to always favor their own survival just as much as any other living thing does. People employed in the public sector are unlikely to vote against policies that threaten their livelihood. This is a bigger problem than we realize because it’s subtle and takes a long time, but every democracy is headed in the same direction. A bigger state, a more complicated system, and fewer individual freedoms. Long term, it seems that all of our systems tend to favor those who know how to play that system and not those who contribute the most value to their fellow man. Proponents of socialist policies often claim that failed socialist states “weren’t really socialist” or that “that wasn’t really socialism.” What most people fail to realize is that we’ve never tried real *capitalism* since we’ve always used more or less inflationary currencies. This might very well be the most skewed narrative of our era. We’re all experiencing real, albeit disguised, socialism every single day. True free market capitalism is what we haven’t experienced yet, and it might turn out to be a very different thing than what we’re told to believe that it is by almost all mainstream media. The validity of the classic right-left scale describing political viewpoints has been debated a lot lately, and alternative scales, like GAL-TAN, the one with an additional Y-axis describing more or less authoritarian tendencies, are popping up in various contexts around the web. After the birth of Bitcoin, there’s a new way to see this. Imagine an origo, a zero point, and a vector pointing to the left of that. *All* politics are arguably on the left because *all* policies need to be funded by taxes, and taxation can be viewed as theft. Taxation can be viewed as theft because, at its core, it’s involuntary. If a person refuses to pay his taxes, there is a threat of violence lurking in the background. Not to mention inflation, which Milton Friedman so elegantly described as “taxation without legislation.” What you do with the portion of your wealth that you have in Bitcoin is another matter altogether. If you take sufficient precautionary privacy measures and you know what you’re doing, your business in Bitcoin is beyond politics altogether. With the introduction of the Lightning Network and other privacy-improving features, it is now impossible for any third party to confiscate your money or even know that you have it, for that matter. This changes the political landscape of every nation on Earth. Bitcoin is much less confiscatable than gold and other scarce assets, which makes it a much better tool for hedging against nation-states. In this sense, Bitcoin obsoletes borders. You can cross any border on Earth with any amount of Bitcoin *in your head*. Think about that! Your Bitcoin exists in every country simultaneously. Any imposed limit on how much money you can carry from one nation to the other is now made obsolete by beautiful mathematics. Bitcoin is sometimes referred to as a “virtual currency.” This is a very inaccurate description. Bitcoin is just mathematics, and mathematics is just about the most real thing there is. There’s nothing virtual about it. Counterintuitive to some, but real nonetheless. The complexity of human societal hierarchies and power structures is described perfectly in a classic children's book, *The Emperor’s New Clothes*, by Hans Christian Andersen. See the world as the kid who points out that the king is naked in the tale, and everything starts to make sense. Everything in human society is man-made. Nations, leaders, laws, political systems. They’re all castles in the air with nothing but a lurking threat of violence to back them up. Bitcoin is a different beast altogether. It enables every individual to verify the validity of the system at all times. If you really think about it, morality is easy. Don’t hurt other people, and don’t steal other people’s stuff. That’s the basic premise. Humans have but two ways of resolving conflict, conversation and violence, and in this sense, to hurt someone can only mean physical violence. This is why free speech is so important and why you should defend people’s right to speak their minds above everything else. It’s not about being able to express yourself. It’s about your right to hear every side of every argument and thus not have to resort to violence should a conflict of interests occur. You can’t limit free speech with just more speech — there’s always a threat of violence behind the limitations. Code, which both Bitcoin and the Internet are entirely made up of, *is speech*. Any limitations or regulations that your government implements in regard to Bitcoin are not only a display of Bitcoin’s censorship resistance but also a test of your government's stance on freedom of expression. A restriction on Bitcoin use is a restriction on free speech. Remember, the only alternative to speech that anyone has is violence. Code is a language, mathematics is a language, and money is a linguistic tool. A linguistic tool we use as a means of expressing value to each other and as a way to transport value through space and time. Any restrictions or regulations regarding how you can express value, for example, making it impossible to buy Bitcoin with your credit card, prove that the money you have in your bank account is not really yours. When people realize this, the demand for Bitcoin goes *up*, not down. If you know what you're doing, there’s no need to fear the regulators. They, on the other hand, have good reason to fear an invention that shamelessly breaks their spell. ### **About the Bitcoin Infinity Academy** The Bitcoin Infinity Academy is an educational project built around [Knut Svanholm](http://primal.net/knut)’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a [video](https://www.youtube.com/@BitcoinInfinityShow) in which Knut and [Luke de Wolf](http://primal.net/luke) discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our [Geyser](https://geyser.fund/project/infinity) page. Signed books, monthly calls, and lots of other benefits are also available. @ 0edc2f47:730cff1b
2025-04-04 03:37:15## Chef's notes This started as a spontaneous kitchen experiment—an amalgamation of recipes from old cookbooks and online finds. My younger daughter wanted to surprise her sister with something quick but fancy ("It's a vibe, Mom."), and this is what we came up with. It’s quickly established itself as a go-to favorite: simple, rich, and deeply satisfying. It serves 4 (or 1, depending on the day; I am not here to judge). Tightly wrapped, it will keep up to 3 days in the fridge, but I bet it won't last that long! ## Details - ⏲️ Prep time: 10 min - 🍳 Cook time: 0 min ## Ingredients - 1 cup (240mL) heavy whipping cream - 1/4 cup (24g) cocoa powder - 5 tbsp (38g) Confectioners (powdered) sugar - 1/4 tsp (1.25mL) vanilla extract (optional) - Flaky sea salt (optional, but excellent) ## Directions 1. 1. Whip the cream until frothy. 2. 2. Sift in cocoa and sugar, fold or gently mix (add vanilla if using). 3. 3. Whip to medium peaks (or stiff peaks, if that's more your thing). Chill and serve (topped with a touch of sea salt if you’re feeling fancy).
@ 0edc2f47:730cff1b
2025-04-04 03:37:15## Chef's notes This started as a spontaneous kitchen experiment—an amalgamation of recipes from old cookbooks and online finds. My younger daughter wanted to surprise her sister with something quick but fancy ("It's a vibe, Mom."), and this is what we came up with. It’s quickly established itself as a go-to favorite: simple, rich, and deeply satisfying. It serves 4 (or 1, depending on the day; I am not here to judge). Tightly wrapped, it will keep up to 3 days in the fridge, but I bet it won't last that long! ## Details - ⏲️ Prep time: 10 min - 🍳 Cook time: 0 min ## Ingredients - 1 cup (240mL) heavy whipping cream - 1/4 cup (24g) cocoa powder - 5 tbsp (38g) Confectioners (powdered) sugar - 1/4 tsp (1.25mL) vanilla extract (optional) - Flaky sea salt (optional, but excellent) ## Directions 1. 1. Whip the cream until frothy. 2. 2. Sift in cocoa and sugar, fold or gently mix (add vanilla if using). 3. 3. Whip to medium peaks (or stiff peaks, if that's more your thing). Chill and serve (topped with a touch of sea salt if you’re feeling fancy). @ fd06f542:8d6d54cd
2025-04-04 02:39:25## 使用nostrbook.com网站 登录和创建用户:  登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。 注册:  可以点击红标位置 生成你的账户。 “确定” 完成注册。 ## 创建书籍 ### 封面的上传  创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。 或者点击浏览 本地图片文件。 ### 标题和作者 正常填写就可以。 书的作者和上传文件人没有一一绑定。 ## 写书  创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。 ### 列出你创建的所有的书籍  点击图标,就可以进入开始写作了。例如《nostrbook站点日记》  如图所示有4个部分 1. (1)关闭按钮,点击就退出编辑,这时候他会提示你保存,如果不需要保存退出,点击 “不保存退出” 2. (2)`大纲` 是编写 你书籍的大纲,这个参考 docsify文档 下面会有例子。 `时间排列`是 你所有为本书写的章节。但是有些章节你可能废弃了,或者暂时不想展示,都会存在 时间排列里面,就是按照你编写的时间倒序排列的。`草稿` 是你暂时存储的内容,没有上传到网络,存在你本地浏览器的缓存里面。 3. (3)这个部分看到的就是你的章节列表,当让你第一次来的这个地方是空的。`新增章节` 下一次就会有内容了。 4. (4)文件名,是我们存储章节的唯一标识。 `readme.md` 和`_sidebar.md` 是系统默认必须有的。因为docsify技术默认需要这2个。
@ fd06f542:8d6d54cd
2025-04-04 02:39:25## 使用nostrbook.com网站 登录和创建用户:  登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。 注册:  可以点击红标位置 生成你的账户。 “确定” 完成注册。 ## 创建书籍 ### 封面的上传  创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。 或者点击浏览 本地图片文件。 ### 标题和作者 正常填写就可以。 书的作者和上传文件人没有一一绑定。 ## 写书  创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。 ### 列出你创建的所有的书籍  点击图标,就可以进入开始写作了。例如《nostrbook站点日记》  如图所示有4个部分 1. (1)关闭按钮,点击就退出编辑,这时候他会提示你保存,如果不需要保存退出,点击 “不保存退出” 2. (2)`大纲` 是编写 你书籍的大纲,这个参考 docsify文档 下面会有例子。 `时间排列`是 你所有为本书写的章节。但是有些章节你可能废弃了,或者暂时不想展示,都会存在 时间排列里面,就是按照你编写的时间倒序排列的。`草稿` 是你暂时存储的内容,没有上传到网络,存在你本地浏览器的缓存里面。 3. (3)这个部分看到的就是你的章节列表,当让你第一次来的这个地方是空的。`新增章节` 下一次就会有内容了。 4. (4)文件名,是我们存储章节的唯一标识。 `readme.md` 和`_sidebar.md` 是系统默认必须有的。因为docsify技术默认需要这2个。 @ c8adf82a:7265ee75
2025-04-04 01:58:49What is knowledge? Why do we need it? Since we were small, our parents/guardian put us in school, worked their asses off to give us elective lessons, some get help until college, some even after college and after professional work. Why is this intelligence thing so sought after? When you were born, you mostly just accepted what your parents said, they say go to school - you go to school, they say go learn the piano - you learn the piano. Of course with a lot of questions and denials, but you do it because you know your parents are doing it for your own good. You can feel the love so you disregard the 'why' and go on with faith Everything starts with why, and for most people maybe the purpose of knowledge is to be smarter, to know more, just because. But for me this sounds utterly useless. One day I will die next to a man with half a brain and we would feel the same exact thing on the ground. Literally being smarter at the end does not matter at all However, I am not saying to just be lazy and foolish. For me the purpose of knowledge is action. The more you learn, the more you know what to do, the more you can be sure you are doing the right thing, the more you can make progress on your own being, etc etc Now, how can you properly learn? Imagine a water bottle. The water bottle's sole purpose is to contain water, but you cannot fill in the water bottle before you open the cap. To learn properly, make sure you open the cap and let all that water pour into you If you are reading this, you are alive. Don't waste your time doing useless stuff and start to make a difference in your life Seize the day
@ c8adf82a:7265ee75
2025-04-04 01:58:49What is knowledge? Why do we need it? Since we were small, our parents/guardian put us in school, worked their asses off to give us elective lessons, some get help until college, some even after college and after professional work. Why is this intelligence thing so sought after? When you were born, you mostly just accepted what your parents said, they say go to school - you go to school, they say go learn the piano - you learn the piano. Of course with a lot of questions and denials, but you do it because you know your parents are doing it for your own good. You can feel the love so you disregard the 'why' and go on with faith Everything starts with why, and for most people maybe the purpose of knowledge is to be smarter, to know more, just because. But for me this sounds utterly useless. One day I will die next to a man with half a brain and we would feel the same exact thing on the ground. Literally being smarter at the end does not matter at all However, I am not saying to just be lazy and foolish. For me the purpose of knowledge is action. The more you learn, the more you know what to do, the more you can be sure you are doing the right thing, the more you can make progress on your own being, etc etc Now, how can you properly learn? Imagine a water bottle. The water bottle's sole purpose is to contain water, but you cannot fill in the water bottle before you open the cap. To learn properly, make sure you open the cap and let all that water pour into you If you are reading this, you are alive. Don't waste your time doing useless stuff and start to make a difference in your life Seize the day @ 306555fe:fd7fdf12
2025-04-04 01:37:14## Blossom Uploader for Nostr In my mini project to publish from Joplin to Nostr, I wanted to move to publishing images in a Joplin note to some internet file hosting. So the obvious is something like imgur or imgbb and these require account creation and use of an API key. The nostr way of doing things is to use blossom and your nsec is the authentication, noice! So I noticed that nostr.build now has a service at https://blossom.band/ It seems to be a very nice service with: > Backed by the time-proven and highly available infrastructure of Nostr.build, > with global reach and a fast CDN network. > Every distinct user's npub gets their own server domain that is not shared by anyone but the > owner of that npub. They also have a free tier which is good for experimentation, their paid plans are at https://nostr.build/plans/ . I'm still yet to figure out of they are a candidate for self-hosting or just for media. That's another research project. Anywayzzz this here article is my test to publish from Joplin for long form posts. When I was doing wordpress posts, I preferred to write up in Joplin with all its note-taking nice-ness, search, tagging, plugins. I've tried [Habla](https://habla.news/) and [YakiHonne](https://www.yakihonne.com/) but I miss my Joplin workflow and tools. So, I've written this in Joplin and using my plugin to test for the article be uploaded as long form (NIP-23) post. Still trying to figure out how to get the markdown transferring across cleanly. Sorry, this is a test. *** --- ________ I made a test project to understand Blossom https://github.com/djinoz/blossom_uploader 🙉 Take #2: Explicity set kind:30023 ## Blossom Uploader for Nostr A Node.js command-line tool to upload images and media files to various services compatible with Nostr notes, with full support for the Blossom protocol. ## Installation ``` npm install ``` ## Usage ``` node blossom_uploader.js [options] <files...> ``` ### Options - `-s, --service <service>`: Upload service to use (default: "imgbb") - `-k, --key <key>`: API key for the service (if required) - `-u, --url <url>`: Custom URL for the service (required for blossom) - `-n, --nsec <nsec>`: Nostr private key (nsec) for blossom authentication - `-d, --debug`: Show debug information - `-o, --output <format>`: Output format: json or url (default: "url") - `-h, --help`: Display help - `-V, --version`: Output the version number ### Examples Upload a single image using ImgBB (default): ``` node blossom_uploader.js path/to/image.jpg ``` Upload using Imgur: ``` node blossom_uploader.js -s imgur image1.png ``` Use your own ImgBB API key: ``` node blossom_uploader.js -s imgbb -k YOUR_API_KEY image.png ``` Upload to a Blossom server using your nsec private key: ``` node blossom_uploader.js -s blossom -u https://blossom.band/upload -n nsec1... image.png ``` Get JSON output: ``` node blossom_uploader.js -o json image.jpg ```
@ 306555fe:fd7fdf12
2025-04-04 01:37:14## Blossom Uploader for Nostr In my mini project to publish from Joplin to Nostr, I wanted to move to publishing images in a Joplin note to some internet file hosting. So the obvious is something like imgur or imgbb and these require account creation and use of an API key. The nostr way of doing things is to use blossom and your nsec is the authentication, noice! So I noticed that nostr.build now has a service at https://blossom.band/ It seems to be a very nice service with: > Backed by the time-proven and highly available infrastructure of Nostr.build, > with global reach and a fast CDN network. > Every distinct user's npub gets their own server domain that is not shared by anyone but the > owner of that npub. They also have a free tier which is good for experimentation, their paid plans are at https://nostr.build/plans/ . I'm still yet to figure out of they are a candidate for self-hosting or just for media. That's another research project. Anywayzzz this here article is my test to publish from Joplin for long form posts. When I was doing wordpress posts, I preferred to write up in Joplin with all its note-taking nice-ness, search, tagging, plugins. I've tried [Habla](https://habla.news/) and [YakiHonne](https://www.yakihonne.com/) but I miss my Joplin workflow and tools. So, I've written this in Joplin and using my plugin to test for the article be uploaded as long form (NIP-23) post. Still trying to figure out how to get the markdown transferring across cleanly. Sorry, this is a test. *** --- ________ I made a test project to understand Blossom https://github.com/djinoz/blossom_uploader 🙉 Take #2: Explicity set kind:30023 ## Blossom Uploader for Nostr A Node.js command-line tool to upload images and media files to various services compatible with Nostr notes, with full support for the Blossom protocol. ## Installation ``` npm install ``` ## Usage ``` node blossom_uploader.js [options] <files...> ``` ### Options - `-s, --service <service>`: Upload service to use (default: "imgbb") - `-k, --key <key>`: API key for the service (if required) - `-u, --url <url>`: Custom URL for the service (required for blossom) - `-n, --nsec <nsec>`: Nostr private key (nsec) for blossom authentication - `-d, --debug`: Show debug information - `-o, --output <format>`: Output format: json or url (default: "url") - `-h, --help`: Display help - `-V, --version`: Output the version number ### Examples Upload a single image using ImgBB (default): ``` node blossom_uploader.js path/to/image.jpg ``` Upload using Imgur: ``` node blossom_uploader.js -s imgur image1.png ``` Use your own ImgBB API key: ``` node blossom_uploader.js -s imgbb -k YOUR_API_KEY image.png ``` Upload to a Blossom server using your nsec private key: ``` node blossom_uploader.js -s blossom -u https://blossom.band/upload -n nsec1... image.png ``` Get JSON output: ``` node blossom_uploader.js -o json image.jpg ``` @ 6389be64:ef439d32
2025-04-03 21:32:58Brewing Biology Episode 1068 of Bitcoin And . . . is LIVE! This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT. LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer. Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue. Biochar’s Hidden Superpower: Adsorption & Buffering Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to: Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts. Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs. Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive. This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates. The Carbon Math Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue. Tools for the Revolution The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks. Bitcoin’s Role in the Loop Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income. The Market Potential Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience. Why This Matters This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet. The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.--- P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting. You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6 originally posted at https://stacker.news/items/933800
@ 6389be64:ef439d32
2025-04-03 21:32:58Brewing Biology Episode 1068 of Bitcoin And . . . is LIVE! This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT. LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer. Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue. Biochar’s Hidden Superpower: Adsorption & Buffering Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to: Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts. Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs. Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive. This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates. The Carbon Math Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue. Tools for the Revolution The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks. Bitcoin’s Role in the Loop Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income. The Market Potential Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience. Why This Matters This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet. The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.--- P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting. You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6 originally posted at https://stacker.news/items/933800 @ 2b42dd42:5049393c
2025-04-03 21:25:46this is a test <img src="https://blossom.primal.net/5029e2735884c4b18875b1e0e378b91133d6a1118c2cf323eef258467b6932c0.png"> end of the test
@ 2b42dd42:5049393c
2025-04-03 21:25:46this is a test <img src="https://blossom.primal.net/5029e2735884c4b18875b1e0e378b91133d6a1118c2cf323eef258467b6932c0.png"> end of the test @ 2ed3596e:98b4cc78
2025-04-03 21:20:27We’re giving you the chance to win even more sats through the Bitcoin (Wishing) Well—just for telling us what you love about Bitcoin Well. Each month, when you leave a review for either the Bitcoin Well portal on **Trustpilot** (include your **WellTag**), or our Bitcoin ATMs and (include your **transaction ID and email**), you’ll be entered for a draw where you can win $210 in bitcoin just for sharing your experience! Whether it’s our self-custody focus, fast Lightning purchases, Lightning referral payouts, private ATM transactions or our unbeatable customer support, we want to hear what makes Bitcoin Well your go-to place for buying, selling, and using bitcoin. ### How to leave your Trustpilot review for our portal 1. Head to our [Trustpilot page](https://ca.trustpilot.com/review/bitcoinwell.com) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your WellTag (or transaction ID)**, in the review so we can add you to the prize draw ### How to leave your google review for one of our ATMs 1. [Google the Bitcoin Well Bitcoin ATM you recently used](https://www.google.com/search?q=bitcoin+well+atm+near+me&oq=bitcoin+well+atm+near+me+&gs_lcrp=EgZjaHJvbWUqBwgAEAAYgAQyBwgAEAAYgAQyCAgBEAAYFhgeMg0IAhAAGIYDGIAEGIoFMgoIAxAAGIAEGKIEMgoIBBAAGIAEGKIEMgoIBRAAGIAEGKIE0gEIMjM2NWowajeoAgCwAgA&sourceid=chrome&ie=UTF-8) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your transaction ID**, in the review so we can add you to the prize draw It’s that easy! Once your review is verified with your welltag or transaction ID, we’ll add your entry to our monthly draw for your chance to win $210 in bitcoin! We’ll announce the winner and the start of each month. Good luck and keep stacking sats! ### What makes Bitcoin Well different Bitcoin Well is on a mission to enable independence. We do this by making it easy to self custody bitcoin. By custodying their own money, our customers are free to do as they wish without begging for permission. By creating a full ecosystem to buy, sell and use your bitcoin to connect with the modern financial world, you are able to have your cake and eat it too - or have your bitcoin in self custody and easily spend it too 🎂. [Create your Bitcoin Well account now →](https://app.bitcoinwell.com/signup) ### Invest in Bitcoin Well We are publicly traded (and love it when our [customers become shareholders!](https://bitcoinwell.com/investors)) and hold ourselves to a high standard of enabling life on a Bitcoin standard. If you want to learn more about Bitcoin Well, please visit our [website](https://bitcoinwell.com/).
@ 2ed3596e:98b4cc78
2025-04-03 21:20:27We’re giving you the chance to win even more sats through the Bitcoin (Wishing) Well—just for telling us what you love about Bitcoin Well. Each month, when you leave a review for either the Bitcoin Well portal on **Trustpilot** (include your **WellTag**), or our Bitcoin ATMs and (include your **transaction ID and email**), you’ll be entered for a draw where you can win $210 in bitcoin just for sharing your experience! Whether it’s our self-custody focus, fast Lightning purchases, Lightning referral payouts, private ATM transactions or our unbeatable customer support, we want to hear what makes Bitcoin Well your go-to place for buying, selling, and using bitcoin. ### How to leave your Trustpilot review for our portal 1. Head to our [Trustpilot page](https://ca.trustpilot.com/review/bitcoinwell.com) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your WellTag (or transaction ID)**, in the review so we can add you to the prize draw ### How to leave your google review for one of our ATMs 1. [Google the Bitcoin Well Bitcoin ATM you recently used](https://www.google.com/search?q=bitcoin+well+atm+near+me&oq=bitcoin+well+atm+near+me+&gs_lcrp=EgZjaHJvbWUqBwgAEAAYgAQyBwgAEAAYgAQyCAgBEAAYFhgeMg0IAhAAGIYDGIAEGIoFMgoIAxAAGIAEGKIEMgoIBBAAGIAEGKIEMgoIBRAAGIAEGKIE0gEIMjM2NWowajeoAgCwAgA&sourceid=chrome&ie=UTF-8) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your transaction ID**, in the review so we can add you to the prize draw It’s that easy! Once your review is verified with your welltag or transaction ID, we’ll add your entry to our monthly draw for your chance to win $210 in bitcoin! We’ll announce the winner and the start of each month. Good luck and keep stacking sats! ### What makes Bitcoin Well different Bitcoin Well is on a mission to enable independence. We do this by making it easy to self custody bitcoin. By custodying their own money, our customers are free to do as they wish without begging for permission. By creating a full ecosystem to buy, sell and use your bitcoin to connect with the modern financial world, you are able to have your cake and eat it too - or have your bitcoin in self custody and easily spend it too 🎂. [Create your Bitcoin Well account now →](https://app.bitcoinwell.com/signup) ### Invest in Bitcoin Well We are publicly traded (and love it when our [customers become shareholders!](https://bitcoinwell.com/investors)) and hold ourselves to a high standard of enabling life on a Bitcoin standard. If you want to learn more about Bitcoin Well, please visit our [website](https://bitcoinwell.com/). @ df67f9a7:2d4fc200
2025-04-03 19:54:29More than just “follows follows” on Nostr, webs of trust algos will ingest increasingly MORE kinds of user generated content in order to map our interactions across the network. Webs of trust will power user discovery, content search, reviews and reccomendations, identity verification, and access to all corners of the Nostr network. Without relying on a central “trust authority” to recommend people and content for us, sovereign Nostr users will make use of “relative trust” scores generated by a wide range of independent apps and services. The problem is, Nostr doesn’t have an opensource library for performing WoT calculations and delivering NIP standard recommendations to users. In order for a “free market” ecosystem of really smart apps and services to thrive, independent developers will need access to extensible “middleware” such as this. ### Project Description I am building a library for independent developers to offer their own interoperable and configurable WoT services and clients. In addition, and as the primary use case, I am also developing a web client for “in person onboarding” to Nostr, which will make use of this library to provide webs of trust recommendations for “invited” users. - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : This is my first project on Nostr, which began a year ago with seed funding from @druid. This web client will leverage “in person” QR invites to generate WoT powered recommendations of follows, apps, and other stuff for new users at their first Nostr touchpoint. The functional MVP release (April ‘25) allows for “instant, anonymous, and fully encrypted” direct messaging and “move in ready” profile creation from a single QR scan. - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs)(developer library) : Working with @straycat last fall, I built an opensource and extensible library for Nostr developers to integrate “web of trust” powered reccomendations into their products and services. The real power behind GrapeRank is its “pluggable” interpreter, allowing any kind of content (not just “follows follows”) to be ingested for WoT scoring, and configurable easily by developers as well as end users. This library is currently in v0.1, “generating and storing usable scores”, and doesn’t yet produce NIP standard outputs for Nostr clients. - [My Grapevine](https://grapevine.my) (algo dashboard) : In addition, I’ve just wrapped up the demo release of a web client by which users and developers can explore the power of the GrapeRank Engine. ### Potential Impact Webs of Trust is how Nostr scales. But so far, Nostr implementations have been ad-hoc and primarily client centered, with no consistency and little choice for end users. The “onboarding and discovery” tools I am developing promise to : - Establish sovereignty for webs of trust users (supporting a “free market” of algo choices), with opensource libraries by which any developer can easily implement WoT powered recommendations. - Accelerate the isolation of bots and bad actors (and improve the “trustiness” of Nostr for everyone else) by streamlining the onboarding of “real world” acquaintances directly into established webs of trust. - Improve “discoverability of users and content” for any user on any client (to consume and take advantage of WoT powered recommendations for any use case, even as the NIP standards for this are still in flux), by providing an algo engine with “pluggable” inputs and outputs. - Pave the way for “global Nostr adoption”, where WoT powered recommendations (and searches) are consistently available for every user across a wide variety of clients. ### Timeline & Milestones 2025 roadmap for “Webs of Trust Onboarding and Discovery” : - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : MVP release : “scan my QR invite to private message me instantly with a ‘move in ready’ account on Nostr”. https://nostrmeet.me/ - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs) (developer library) : 1.0 release : “expanded inputs and output WoT scores to Nostr NIPs and other stuff” for consumption by clients and relays. https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs - [My Grapevine](https://grapevine.my) (algo dashboard) : 1.0 release : “algo usage and configuration webapp with API endpoints” for end users to setup GrapeRank scoring for consumption by their own clients and relays. https://grapevine.my/ - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : 1.0 release : first GrapeRank integration, offering “follow and app recommendations for invited users”, customizable per-invite for Nostr advocates. https://nostrmeet.me/ ### Prior contributions - Last spring I hosted panel discussions and [wrote articles on Nostr](https://primal.net/p/npub1manlnflyzyjhgh970t8mmngrdytcp3jrmaa66u846ggg7t20cgqqvyn9tn#reads) exploring how to build “sovereign webs of trust”, where end users can have control over which algorithms to use, and what defines “trust”. - I contributed [gift wrap encryption](https://github.com/nostr-dev-kit/ndk/commit/82b60c3b6ae2f38bde0e542d31bfa10d58d08116) to NDK. - I am also authoring [gift wrapped direct messaging and chat room](https://github.com/nostr-dev-kit/ndk/pulls?q=is%3Apr+author%3Amanimejia) modules for NDK. - Last July, I attended The Bitcoin Conference on an OpenSource pass to raise funds for my onboarding client. I onboarded many Bitcoiners to Nostr, and made valuable connections at Bitcoin Park. ### About Me I discovered Nostr in September ‘23 as a freelance web developer, after years of looking for a “sovereignty respecting” social media on which to build apps. With this came my first purchase of Bitcoin. By December of that year, I was settled on “open source freedom tech” (Nostr and Bitcoin) as the new direction for my career. As a web professional for 20+ years, I know the importance of “proof of work” and being connected. For the last 18 months, I have been establishing myself as a builder in this community. This pivot has not been easy, but it has been rewarding and necessary. After so many years building private tech for other people, I finally have a chance to build freedom tech for everyone. I have finally come home to my peeps and my purpose. Thank you for considering this application for funding.
@ df67f9a7:2d4fc200
2025-04-03 19:54:29More than just “follows follows” on Nostr, webs of trust algos will ingest increasingly MORE kinds of user generated content in order to map our interactions across the network. Webs of trust will power user discovery, content search, reviews and reccomendations, identity verification, and access to all corners of the Nostr network. Without relying on a central “trust authority” to recommend people and content for us, sovereign Nostr users will make use of “relative trust” scores generated by a wide range of independent apps and services. The problem is, Nostr doesn’t have an opensource library for performing WoT calculations and delivering NIP standard recommendations to users. In order for a “free market” ecosystem of really smart apps and services to thrive, independent developers will need access to extensible “middleware” such as this. ### Project Description I am building a library for independent developers to offer their own interoperable and configurable WoT services and clients. In addition, and as the primary use case, I am also developing a web client for “in person onboarding” to Nostr, which will make use of this library to provide webs of trust recommendations for “invited” users. - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : This is my first project on Nostr, which began a year ago with seed funding from @druid. This web client will leverage “in person” QR invites to generate WoT powered recommendations of follows, apps, and other stuff for new users at their first Nostr touchpoint. The functional MVP release (April ‘25) allows for “instant, anonymous, and fully encrypted” direct messaging and “move in ready” profile creation from a single QR scan. - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs)(developer library) : Working with @straycat last fall, I built an opensource and extensible library for Nostr developers to integrate “web of trust” powered reccomendations into their products and services. The real power behind GrapeRank is its “pluggable” interpreter, allowing any kind of content (not just “follows follows”) to be ingested for WoT scoring, and configurable easily by developers as well as end users. This library is currently in v0.1, “generating and storing usable scores”, and doesn’t yet produce NIP standard outputs for Nostr clients. - [My Grapevine](https://grapevine.my) (algo dashboard) : In addition, I’ve just wrapped up the demo release of a web client by which users and developers can explore the power of the GrapeRank Engine. ### Potential Impact Webs of Trust is how Nostr scales. But so far, Nostr implementations have been ad-hoc and primarily client centered, with no consistency and little choice for end users. The “onboarding and discovery” tools I am developing promise to : - Establish sovereignty for webs of trust users (supporting a “free market” of algo choices), with opensource libraries by which any developer can easily implement WoT powered recommendations. - Accelerate the isolation of bots and bad actors (and improve the “trustiness” of Nostr for everyone else) by streamlining the onboarding of “real world” acquaintances directly into established webs of trust. - Improve “discoverability of users and content” for any user on any client (to consume and take advantage of WoT powered recommendations for any use case, even as the NIP standards for this are still in flux), by providing an algo engine with “pluggable” inputs and outputs. - Pave the way for “global Nostr adoption”, where WoT powered recommendations (and searches) are consistently available for every user across a wide variety of clients. ### Timeline & Milestones 2025 roadmap for “Webs of Trust Onboarding and Discovery” : - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : MVP release : “scan my QR invite to private message me instantly with a ‘move in ready’ account on Nostr”. https://nostrmeet.me/ - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs) (developer library) : 1.0 release : “expanded inputs and output WoT scores to Nostr NIPs and other stuff” for consumption by clients and relays. https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs - [My Grapevine](https://grapevine.my) (algo dashboard) : 1.0 release : “algo usage and configuration webapp with API endpoints” for end users to setup GrapeRank scoring for consumption by their own clients and relays. https://grapevine.my/ - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : 1.0 release : first GrapeRank integration, offering “follow and app recommendations for invited users”, customizable per-invite for Nostr advocates. https://nostrmeet.me/ ### Prior contributions - Last spring I hosted panel discussions and [wrote articles on Nostr](https://primal.net/p/npub1manlnflyzyjhgh970t8mmngrdytcp3jrmaa66u846ggg7t20cgqqvyn9tn#reads) exploring how to build “sovereign webs of trust”, where end users can have control over which algorithms to use, and what defines “trust”. - I contributed [gift wrap encryption](https://github.com/nostr-dev-kit/ndk/commit/82b60c3b6ae2f38bde0e542d31bfa10d58d08116) to NDK. - I am also authoring [gift wrapped direct messaging and chat room](https://github.com/nostr-dev-kit/ndk/pulls?q=is%3Apr+author%3Amanimejia) modules for NDK. - Last July, I attended The Bitcoin Conference on an OpenSource pass to raise funds for my onboarding client. I onboarded many Bitcoiners to Nostr, and made valuable connections at Bitcoin Park. ### About Me I discovered Nostr in September ‘23 as a freelance web developer, after years of looking for a “sovereignty respecting” social media on which to build apps. With this came my first purchase of Bitcoin. By December of that year, I was settled on “open source freedom tech” (Nostr and Bitcoin) as the new direction for my career. As a web professional for 20+ years, I know the importance of “proof of work” and being connected. For the last 18 months, I have been establishing myself as a builder in this community. This pivot has not been easy, but it has been rewarding and necessary. After so many years building private tech for other people, I finally have a chance to build freedom tech for everyone. I have finally come home to my peeps and my purpose. Thank you for considering this application for funding. @ 7d33ba57:1b82db35
2025-04-03 17:36:08Zadar is a coastal city in northern Dalmatia, known for its rich Roman and Venetian history, stunning sunsets, and unique modern attractions like the Sea Organ and Sun Salutation. With ancient ruins, beautiful beaches, and a lively Old Town, Zadar offers a less crowded but equally charming alternative** to Split and Dubrovnik.  ## **🏛️ Top Things to See & Do in Zadar** ### **1️⃣ Explore Zadar Old Town 🏰** - Walk through **narrow, stone-paved streets**, surrounded by **Roman and medieval architecture**. - Visit **People’s Square (Narodni Trg)** – The **heart of Zadar’s Old Town**, filled with lively cafés. ### **2️⃣ Visit the Sea Organ & Sun Salutation 🎶🌞** - **Sea Organ** – A one-of-a-kind **musical instrument**, where waves create **natural melodies**. - **Sun Salutation** – A large **solar-powered light display**, best seen at sunset. - **Alfred Hitchcock once called Zadar’s sunset “the most beautiful in the world.”** 🌅  ### **3️⃣ Admire St. Donatus Church & Roman Forum ⛪** - **St. Donatus (9th century)** – A unique, round **Byzantine-style church** with great acoustics. - **Roman Forum** – The remains of an ancient Roman marketplace, built in the **1st century BC**. ### **4️⃣ Climb the Bell Tower of St. Anastasia’s Cathedral 🔔** - Enjoy **spectacular views** over Zadar’s rooftops and the Adriatic. - One of the **tallest church towers in Croatia**.  ### **5️⃣ Relax at Zadar’s Best Beaches 🏖️** - **Kolovare Beach** – The most popular **city beach**, just a short walk from the Old Town. - **Borik Beach** – A **sandy beach with shallow waters**, ideal for families. - **Punta Bajlo** – A more **natural and peaceful spot**, great for a quiet swim. ### **6️⃣ Take a Day Trip to Kornati National Park ⛵** - A **beautiful archipelago of 89 islands**, perfect for **boating, swimming, and snorkeling**. - Join a **boat tour from Zadar** to explore the **untouched nature of the Adriatic**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Black Risotto (Crni Rižot)** – A delicious squid-ink seafood dish. 🦑 - **Pag Cheese (Paški Sir)** – A famous **sheep’s milk cheese from Pag Island**. 🧀 - **Grilled Adriatic Fish** – Freshly caught and served with **olive oil & Dalmatian herbs**. 🐟  ## **🚗 How to Get to Zadar** ✈️ **By Air:** - **Zadar Airport (ZAD)** is **just 15 minutes from the city center**. 🚘 **By Car:** - **From Split:** ~1.5 hours (160 km) - **From Zagreb:** ~2.5 hours (285 km) 🚌 **By Bus:** Regular buses from **Split, Zagreb, Dubrovnik, and Plitvice Lakes**. ⛴️ **By Ferry:** Ferries connect Zadar to nearby islands like **Ugljan, Dugi Otok, and Pašman**.  ## **💡 Tips for Visiting Zadar** ✅ **Best time to visit?** **May–October** for warm weather & island trips ☀️ ✅ **Stay near the Old Town** – Everything is within walking distance 🏡 ✅ **Catch the sunset at the Sea Organ** – It’s a must-do experience 🌊🎶 ✅ **Take a ferry to Ugljan Island** for a day of beaches & cycling 🚢🚴♂️ ✅ **Book Kornati boat tours in advance** – They sell out fast in summer! ⛵ 
@ 7d33ba57:1b82db35
2025-04-03 17:36:08Zadar is a coastal city in northern Dalmatia, known for its rich Roman and Venetian history, stunning sunsets, and unique modern attractions like the Sea Organ and Sun Salutation. With ancient ruins, beautiful beaches, and a lively Old Town, Zadar offers a less crowded but equally charming alternative** to Split and Dubrovnik.  ## **🏛️ Top Things to See & Do in Zadar** ### **1️⃣ Explore Zadar Old Town 🏰** - Walk through **narrow, stone-paved streets**, surrounded by **Roman and medieval architecture**. - Visit **People’s Square (Narodni Trg)** – The **heart of Zadar’s Old Town**, filled with lively cafés. ### **2️⃣ Visit the Sea Organ & Sun Salutation 🎶🌞** - **Sea Organ** – A one-of-a-kind **musical instrument**, where waves create **natural melodies**. - **Sun Salutation** – A large **solar-powered light display**, best seen at sunset. - **Alfred Hitchcock once called Zadar’s sunset “the most beautiful in the world.”** 🌅  ### **3️⃣ Admire St. Donatus Church & Roman Forum ⛪** - **St. Donatus (9th century)** – A unique, round **Byzantine-style church** with great acoustics. - **Roman Forum** – The remains of an ancient Roman marketplace, built in the **1st century BC**. ### **4️⃣ Climb the Bell Tower of St. Anastasia’s Cathedral 🔔** - Enjoy **spectacular views** over Zadar’s rooftops and the Adriatic. - One of the **tallest church towers in Croatia**.  ### **5️⃣ Relax at Zadar’s Best Beaches 🏖️** - **Kolovare Beach** – The most popular **city beach**, just a short walk from the Old Town. - **Borik Beach** – A **sandy beach with shallow waters**, ideal for families. - **Punta Bajlo** – A more **natural and peaceful spot**, great for a quiet swim. ### **6️⃣ Take a Day Trip to Kornati National Park ⛵** - A **beautiful archipelago of 89 islands**, perfect for **boating, swimming, and snorkeling**. - Join a **boat tour from Zadar** to explore the **untouched nature of the Adriatic**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Black Risotto (Crni Rižot)** – A delicious squid-ink seafood dish. 🦑 - **Pag Cheese (Paški Sir)** – A famous **sheep’s milk cheese from Pag Island**. 🧀 - **Grilled Adriatic Fish** – Freshly caught and served with **olive oil & Dalmatian herbs**. 🐟  ## **🚗 How to Get to Zadar** ✈️ **By Air:** - **Zadar Airport (ZAD)** is **just 15 minutes from the city center**. 🚘 **By Car:** - **From Split:** ~1.5 hours (160 km) - **From Zagreb:** ~2.5 hours (285 km) 🚌 **By Bus:** Regular buses from **Split, Zagreb, Dubrovnik, and Plitvice Lakes**. ⛴️ **By Ferry:** Ferries connect Zadar to nearby islands like **Ugljan, Dugi Otok, and Pašman**.  ## **💡 Tips for Visiting Zadar** ✅ **Best time to visit?** **May–October** for warm weather & island trips ☀️ ✅ **Stay near the Old Town** – Everything is within walking distance 🏡 ✅ **Catch the sunset at the Sea Organ** – It’s a must-do experience 🌊🎶 ✅ **Take a ferry to Ugljan Island** for a day of beaches & cycling 🚢🚴♂️ ✅ **Book Kornati boat tours in advance** – They sell out fast in summer! ⛵  @ 000002de:c05780a7
2025-04-03 17:27:03### I score zero points. How about you? https://m.primal.net/QDDi.jpg I almost called this a boomer test but its more of a Gen X test. __Credit to Jack Spirko for sharing this on Twitter.__ originally posted at https://stacker.news/items/933537
@ 000002de:c05780a7
2025-04-03 17:27:03### I score zero points. How about you? https://m.primal.net/QDDi.jpg I almost called this a boomer test but its more of a Gen X test. __Credit to Jack Spirko for sharing this on Twitter.__ originally posted at https://stacker.news/items/933537 @ 5708b1f6:208df3b8
2025-04-03 15:25:33The role and significance of music naturally varies from person to person. For some, it is counted among the most important things in life. For others, it may be a superfluous additive of limited value. Due to this difference in perception relating to music, it may be difficult for some individuals to recognize the benefits of compiling a personalized music playlist. However, the value of music as a therapeutic tool for people already suffering from advanced dementia has been repeatedly demonstrated, and sometimes with astounding, although temporary, results. The internet is full of studies and stories, and YouTube searches yield an abundance of video evidence ranging from clinical studies to anecdotal family recordings of elderly relatives. All of these data and anecdotes point to a compelling suggestion and an exciting conclusion: music appreciation has tremendous potential as a supplemental activity for mental health maintenance. With insights gained from the study of neuroplasticity, the neurological benefits for musicians and performers are easy to see, but less clear is the fact that mere exposure to music as a casual listener can be of profound psychological importance, even for individuals who don’t consider themselves to be music lovers. The transformative effect of music is on full display in many of the available videos on YouTube. We can simply search “dementia music,” or ‘Alzheimer’s music” for fast, relevant results. In video after video, we can see elderly subjects who may be slow to speak, detached, disoriented, barely-intelligible, or unresponsive. In care facilities and at gatherings with families, they are interviewed about their youth, and about their feelings related to music. Many of the videos first show footage of the individual’s normal daily cognitive state, and them listening and responding to the questions, followed by a period of music listening, and then another brief, post-music discussion. The transformation of mental states tends to be very clear when we compare the quality of their cognitive performance before and after the introduction of music. People remark that “a light has been turned back on,” or “his personality returned,” or “it’s as if the person has woken up from sleep.” Unfortunately, these positive responses are only temporary, and music does not have the power to permanently reverse the symptoms and pathology of advanced dementia and age-related cognitive decline. Also there is no guarantee it will work for every person, or to what degree. Nevertheless, it does not mean that music as therapy is completely without value. In fact, it can be quite the opposite. When the response is positive, the event can have multiple benefits, and may even be a therapeutic experience for certain listeners. Faces once despondent or vacant become animated and radiant. Long lost smiles return from faraway times and places. Memories and associations from previous ages shake loose and rise to the surface. Many listeners were asked to recount their experiences related to the songs and the time in life with which they were primarily associated. Some of them were able to describe events, places, people, emotions, and reactions with a degree of clarity, dexterity, and articulation that was completely inconsistent with their medical diagnosis and their cognitive performance prior to hearing the music. The song quite literally revives the personality that makes the person, temporarily and superficially reversing the undoing of the mind. For a mind that is coming undone, music as therapy has potential to mitigate suffering and confusion, provide moments of joy and enthusiasm, and ease the transition into and experience of the end-of-life period that awaits all who are fortunate enough to “die of natural causes” in old age. The benefits described above are specific to “treatment” recipients, but the merit of music as therapy cascades into the lives of everyone involved. Doctors and caretakers are uplifted and encouraged by success stories, which contributes to further proliferation and advancement of music as therapy. More critically, it can have a profound impact on families of dementia patients. In some cases, relatives get a chance to communicate with their loved ones again. Grandchildren have a window of opportunity to learn more, directly from their grandparents, about the youthful experiences and memories of past generations. It’s clear that generational bonds are also strengthened, which can positively impact the future prospects of the young generation as they in turn grow old, and lay new groundwork for generations that follow. It is unfortunate that some elderly individuals seem to derive less cognitive benefit than others from music therapy. It is not entirely certain why this is so, because there are many factors to consider, but two of the clearest factors are a person’s degree of cognitive decline, and their degree of interest in and enthusiasm for music in general. While these are the most popular metrics by which to judge the potential effectiveness and suitability of music as therapy for a given individual, by far the most important consideration is relevance to each particular person’s life experiences. This is the opportunity to finally state the obvious: It’s not possible to simply pick any song at random and expect it to have a beneficial effect on the cognitive function of every person who hears it. It’s not as if there’s a Britney Spears song that sparks joy in the heart of every soul on Earth. And the legend of Bill and Ted’s ultimate song that united the world could never be a true story (also because, as we finally learned in 2020, it was not two men and a song that united the world, but rather, the world uniting together to create that song.) However, everyone in the world can make their own playlist custom-tailored to their individual life, experiences, and memories, and some of those playlists might have a song or two by Britney Spears, or even some from one of the “Bill and Ted” soundtracks. Throughout my decades of music appreciation, an ever-growing level of respect for the enduring spirit of music has overwhelmed me, and it’s clear that no song will ever be loved by all. But every song will be loved by some, certainly at least by someone, or it would cease to exist. This is why a personalized playlist is infinitely more valuable than randomly selected songs, and we can see the truth of this claim upon close examination of recorded interviews with the elderly subjects. The songs that triggered the greatest reactions were songs that interviewees felt strong connections to, based primarily on the song’s associations to the time and place, as well as the emotional context imprinted on the memory of the events surrounding the songs. This simply means that songs for which we have emotional attachments and vivid memories are songs that invigorate our neural circuits, activating cognitive pathways and opening doors of memory similar to how olfactory sensations can trigger a memory or a sense of déjà vu. There are some exceptions, but a lot of these songs are from a person’s formative years, particularly early developmental years and their teenage period. This comes as no surprise to the discerning neuroplastician, because these are periods of life when neural plasticity is most fluid, neural development and refinement functions are most active and receptive, and the degree of exciting novelty in life tends to be highest when we are young and inexperienced. Novelty and emotion are critical components of memory formation and whether a given experience will be memorable or not. Something completely new (novelty) can be memorable if it commands your attention, or derails you from your usual pattern of behavior. Similarly, the content of a tedious lecture may be harder to recall without taking notes, while that of an exciting, fun, and funny, interactive lesson has a greater chance of being memorable, and recalled with more clarity and detail (emotion). When it comes to music, the connection to novelty and emotion is crystal clear. The first time you ever heard that song, it was new and your emotional response was strong. You might even remember the events of that first time you heard it, but not necessarily. Your emotional attachment to the song may have developed later on, when you heard it playing at a party, on one of the most memorable nights of your teenage life, for example. Perhaps it’s just a song (or songs) your parents played a lot when you were young, and it could be a song you yourself heard many times, and looking back realized it holds a special place in your heart, for whatever reason. There are also songs that are special to romantic couples (This song was playing when we…; This is our song; We were together the first time we heard this song; etc.) and these songs, for obvious reasons, can be added to a personalized music playlist at any time in life, as new and old songs take on added personal significance in various ways. There are a multitude of ways that novelty and emotion can combine to form experiences worth remembering, by which memories are made, and if these experiences are imprinted with a musical stamp, the song stamped onto the memory is likely to remain just as memorable as the event itself, and conversely, listening to the song has the potential to vivify the memories and feelings of nostalgia related to the song. Therefore, as a preventative measure we can implement now, and an insurance policy we may benefit from later, it is advisable that each person should endeavor to compile their own personal, individualized cognitive reserve playlist. When speaking to someone about this idea, they responded, “But what’s the hurry? After all, you’re still quite young.” Just then, it spontaneously occurred to me that a traumatic head injury could befall me the following day or any day hence, and the simple point that “it’s never too early” was well taken. To create your own cognitive reserve playlist, it is helpful to have a few guiding parameters. Most important of all is to keep an open mind without setting anything in stone. It’s not necessary to finalize the list immediately, if ever. This is a project that deserves your thoughtful consideration, so you deserve to be allowed to take your time. It’s better to get the list populated with your definite favorites, and as many others that come to mind, just to kick-start the process. Besides, due to the virtually infinite number of songs and compositions in existence, we will never be able to make the perfect list in one day, one month, or even one year. We can always revisit the list and make changes later, because our minds cannot retrieve all the data at once. We must go about our business of carrying on, and wait for it to come to us. (It’s guaranteed to be worth the wait, so never fret about it.) You may even find yourself removing one of those “definite favorites” from the list, which is welcome and fine, because it’s not merely a list of your favorite songs. Being a “favorite” is just one of multiple indicators that a song might be appropriate for a cognitive reserve playlist. “Memorable” is another key word. There are still other factors that determine a song’s suitability for a personal playlist, such as a song that isn’t a personal favorite, but which nevertheless evokes a strong emotional response in some other way. This is best described as nostalgia, and nostalgic emotions are powerful anchors for memories. So any song that arouses some sense of nostalgia also has the power to arouse the memory of events, places, times, and other details tied to that nostalgia. To know what songs are nostalgic for you and add them to your list today, may help you if a time should come that you need music as therapy in order to trigger your memory and cognitive function. It is because of nostalgia that many songs from our youth are good candidates for inclusion on the playlist. Songs that were popular on the radio or TV when we were children, theme songs from popular television programs that are unforgettable for us, and songs that acted as the soundtrack to our lives, so to speak, while growing into childhood, and then blossoming again from adolescence into adulthood. This period is rich with music of great significance to our personal center. It is my sincere hope that all people earnestly endeavor to compile their own personalized cognitive reserve playlists, and encourage their loved ones to do the same. Maybe it can help those who suffer to better cope with the condition. Perhaps starting this project now, and focusing on mental health now can be a significant contributing factor to developing robust cognitive reserve in the first place, thereby heading off the worst of what this condition can throw at us, and delaying it until later. And of course, not only should we create the lists, but it’s highly recommended that we also play the songs frequently, and dance to them as well, preferably. It is in the interest of your future health, ability, mobility, enjoyment, and ease of living that I offer this potentially beneficial suggestion, and I am grateful that you have taken the time to hear me out regarding my passion about the restorative and healing properties of music, as they relate to the broader topic of neuroplasticity. So on that note, shall we press play and dance?
@ 5708b1f6:208df3b8
2025-04-03 15:25:33The role and significance of music naturally varies from person to person. For some, it is counted among the most important things in life. For others, it may be a superfluous additive of limited value. Due to this difference in perception relating to music, it may be difficult for some individuals to recognize the benefits of compiling a personalized music playlist. However, the value of music as a therapeutic tool for people already suffering from advanced dementia has been repeatedly demonstrated, and sometimes with astounding, although temporary, results. The internet is full of studies and stories, and YouTube searches yield an abundance of video evidence ranging from clinical studies to anecdotal family recordings of elderly relatives. All of these data and anecdotes point to a compelling suggestion and an exciting conclusion: music appreciation has tremendous potential as a supplemental activity for mental health maintenance. With insights gained from the study of neuroplasticity, the neurological benefits for musicians and performers are easy to see, but less clear is the fact that mere exposure to music as a casual listener can be of profound psychological importance, even for individuals who don’t consider themselves to be music lovers. The transformative effect of music is on full display in many of the available videos on YouTube. We can simply search “dementia music,” or ‘Alzheimer’s music” for fast, relevant results. In video after video, we can see elderly subjects who may be slow to speak, detached, disoriented, barely-intelligible, or unresponsive. In care facilities and at gatherings with families, they are interviewed about their youth, and about their feelings related to music. Many of the videos first show footage of the individual’s normal daily cognitive state, and them listening and responding to the questions, followed by a period of music listening, and then another brief, post-music discussion. The transformation of mental states tends to be very clear when we compare the quality of their cognitive performance before and after the introduction of music. People remark that “a light has been turned back on,” or “his personality returned,” or “it’s as if the person has woken up from sleep.” Unfortunately, these positive responses are only temporary, and music does not have the power to permanently reverse the symptoms and pathology of advanced dementia and age-related cognitive decline. Also there is no guarantee it will work for every person, or to what degree. Nevertheless, it does not mean that music as therapy is completely without value. In fact, it can be quite the opposite. When the response is positive, the event can have multiple benefits, and may even be a therapeutic experience for certain listeners. Faces once despondent or vacant become animated and radiant. Long lost smiles return from faraway times and places. Memories and associations from previous ages shake loose and rise to the surface. Many listeners were asked to recount their experiences related to the songs and the time in life with which they were primarily associated. Some of them were able to describe events, places, people, emotions, and reactions with a degree of clarity, dexterity, and articulation that was completely inconsistent with their medical diagnosis and their cognitive performance prior to hearing the music. The song quite literally revives the personality that makes the person, temporarily and superficially reversing the undoing of the mind. For a mind that is coming undone, music as therapy has potential to mitigate suffering and confusion, provide moments of joy and enthusiasm, and ease the transition into and experience of the end-of-life period that awaits all who are fortunate enough to “die of natural causes” in old age. The benefits described above are specific to “treatment” recipients, but the merit of music as therapy cascades into the lives of everyone involved. Doctors and caretakers are uplifted and encouraged by success stories, which contributes to further proliferation and advancement of music as therapy. More critically, it can have a profound impact on families of dementia patients. In some cases, relatives get a chance to communicate with their loved ones again. Grandchildren have a window of opportunity to learn more, directly from their grandparents, about the youthful experiences and memories of past generations. It’s clear that generational bonds are also strengthened, which can positively impact the future prospects of the young generation as they in turn grow old, and lay new groundwork for generations that follow. It is unfortunate that some elderly individuals seem to derive less cognitive benefit than others from music therapy. It is not entirely certain why this is so, because there are many factors to consider, but two of the clearest factors are a person’s degree of cognitive decline, and their degree of interest in and enthusiasm for music in general. While these are the most popular metrics by which to judge the potential effectiveness and suitability of music as therapy for a given individual, by far the most important consideration is relevance to each particular person’s life experiences. This is the opportunity to finally state the obvious: It’s not possible to simply pick any song at random and expect it to have a beneficial effect on the cognitive function of every person who hears it. It’s not as if there’s a Britney Spears song that sparks joy in the heart of every soul on Earth. And the legend of Bill and Ted’s ultimate song that united the world could never be a true story (also because, as we finally learned in 2020, it was not two men and a song that united the world, but rather, the world uniting together to create that song.) However, everyone in the world can make their own playlist custom-tailored to their individual life, experiences, and memories, and some of those playlists might have a song or two by Britney Spears, or even some from one of the “Bill and Ted” soundtracks. Throughout my decades of music appreciation, an ever-growing level of respect for the enduring spirit of music has overwhelmed me, and it’s clear that no song will ever be loved by all. But every song will be loved by some, certainly at least by someone, or it would cease to exist. This is why a personalized playlist is infinitely more valuable than randomly selected songs, and we can see the truth of this claim upon close examination of recorded interviews with the elderly subjects. The songs that triggered the greatest reactions were songs that interviewees felt strong connections to, based primarily on the song’s associations to the time and place, as well as the emotional context imprinted on the memory of the events surrounding the songs. This simply means that songs for which we have emotional attachments and vivid memories are songs that invigorate our neural circuits, activating cognitive pathways and opening doors of memory similar to how olfactory sensations can trigger a memory or a sense of déjà vu. There are some exceptions, but a lot of these songs are from a person’s formative years, particularly early developmental years and their teenage period. This comes as no surprise to the discerning neuroplastician, because these are periods of life when neural plasticity is most fluid, neural development and refinement functions are most active and receptive, and the degree of exciting novelty in life tends to be highest when we are young and inexperienced. Novelty and emotion are critical components of memory formation and whether a given experience will be memorable or not. Something completely new (novelty) can be memorable if it commands your attention, or derails you from your usual pattern of behavior. Similarly, the content of a tedious lecture may be harder to recall without taking notes, while that of an exciting, fun, and funny, interactive lesson has a greater chance of being memorable, and recalled with more clarity and detail (emotion). When it comes to music, the connection to novelty and emotion is crystal clear. The first time you ever heard that song, it was new and your emotional response was strong. You might even remember the events of that first time you heard it, but not necessarily. Your emotional attachment to the song may have developed later on, when you heard it playing at a party, on one of the most memorable nights of your teenage life, for example. Perhaps it’s just a song (or songs) your parents played a lot when you were young, and it could be a song you yourself heard many times, and looking back realized it holds a special place in your heart, for whatever reason. There are also songs that are special to romantic couples (This song was playing when we…; This is our song; We were together the first time we heard this song; etc.) and these songs, for obvious reasons, can be added to a personalized music playlist at any time in life, as new and old songs take on added personal significance in various ways. There are a multitude of ways that novelty and emotion can combine to form experiences worth remembering, by which memories are made, and if these experiences are imprinted with a musical stamp, the song stamped onto the memory is likely to remain just as memorable as the event itself, and conversely, listening to the song has the potential to vivify the memories and feelings of nostalgia related to the song. Therefore, as a preventative measure we can implement now, and an insurance policy we may benefit from later, it is advisable that each person should endeavor to compile their own personal, individualized cognitive reserve playlist. When speaking to someone about this idea, they responded, “But what’s the hurry? After all, you’re still quite young.” Just then, it spontaneously occurred to me that a traumatic head injury could befall me the following day or any day hence, and the simple point that “it’s never too early” was well taken. To create your own cognitive reserve playlist, it is helpful to have a few guiding parameters. Most important of all is to keep an open mind without setting anything in stone. It’s not necessary to finalize the list immediately, if ever. This is a project that deserves your thoughtful consideration, so you deserve to be allowed to take your time. It’s better to get the list populated with your definite favorites, and as many others that come to mind, just to kick-start the process. Besides, due to the virtually infinite number of songs and compositions in existence, we will never be able to make the perfect list in one day, one month, or even one year. We can always revisit the list and make changes later, because our minds cannot retrieve all the data at once. We must go about our business of carrying on, and wait for it to come to us. (It’s guaranteed to be worth the wait, so never fret about it.) You may even find yourself removing one of those “definite favorites” from the list, which is welcome and fine, because it’s not merely a list of your favorite songs. Being a “favorite” is just one of multiple indicators that a song might be appropriate for a cognitive reserve playlist. “Memorable” is another key word. There are still other factors that determine a song’s suitability for a personal playlist, such as a song that isn’t a personal favorite, but which nevertheless evokes a strong emotional response in some other way. This is best described as nostalgia, and nostalgic emotions are powerful anchors for memories. So any song that arouses some sense of nostalgia also has the power to arouse the memory of events, places, times, and other details tied to that nostalgia. To know what songs are nostalgic for you and add them to your list today, may help you if a time should come that you need music as therapy in order to trigger your memory and cognitive function. It is because of nostalgia that many songs from our youth are good candidates for inclusion on the playlist. Songs that were popular on the radio or TV when we were children, theme songs from popular television programs that are unforgettable for us, and songs that acted as the soundtrack to our lives, so to speak, while growing into childhood, and then blossoming again from adolescence into adulthood. This period is rich with music of great significance to our personal center. It is my sincere hope that all people earnestly endeavor to compile their own personalized cognitive reserve playlists, and encourage their loved ones to do the same. Maybe it can help those who suffer to better cope with the condition. Perhaps starting this project now, and focusing on mental health now can be a significant contributing factor to developing robust cognitive reserve in the first place, thereby heading off the worst of what this condition can throw at us, and delaying it until later. And of course, not only should we create the lists, but it’s highly recommended that we also play the songs frequently, and dance to them as well, preferably. It is in the interest of your future health, ability, mobility, enjoyment, and ease of living that I offer this potentially beneficial suggestion, and I am grateful that you have taken the time to hear me out regarding my passion about the restorative and healing properties of music, as they relate to the broader topic of neuroplasticity. So on that note, shall we press play and dance? @ e4950c93:1b99eccd
2025-04-03 14:57:41Découvrez les matières utilisées ou non dans les produits référencés sur ce site. ### ✅ Matières naturelles Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire. #### 🌱 Principaux critères : - Biodégradabilité - Non-toxicité - Présence naturelle et minimum de transformation #### 🔍 Liste des matières naturelles : - Caoutchouc naturel - Chanvre - Coton - Cuir - Liège - Lin - Laine - Soie - Terre - … (Autres matières) ⚠️ Bien que naturelles, ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière. Les versions biologiques, sans traitement chimique… de ces matieres sont privilégiées pour référencer les produits sur ce site. Les versions "conventionnelles" ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits. --- ### 🚫 Matières non naturelles Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie. #### 📌 Principaux problèmes : - Émissions de microplastiques - Dépendance aux énergies fossiles - Mauvaise biodégradabilité #### 🔍 Liste des matières non naturelles : - Polyester - Polyamide - Acrylique - Élasthanne - Viscose - Silicone - … (Ajouter les autres matières) ⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque : - elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et - aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits. Dans ce cas, un avertissement est alors affiché sur la fiche du produit.
@ e4950c93:1b99eccd
2025-04-03 14:57:41Découvrez les matières utilisées ou non dans les produits référencés sur ce site. ### ✅ Matières naturelles Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire. #### 🌱 Principaux critères : - Biodégradabilité - Non-toxicité - Présence naturelle et minimum de transformation #### 🔍 Liste des matières naturelles : - Caoutchouc naturel - Chanvre - Coton - Cuir - Liège - Lin - Laine - Soie - Terre - … (Autres matières) ⚠️ Bien que naturelles, ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière. Les versions biologiques, sans traitement chimique… de ces matieres sont privilégiées pour référencer les produits sur ce site. Les versions "conventionnelles" ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits. --- ### 🚫 Matières non naturelles Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie. #### 📌 Principaux problèmes : - Émissions de microplastiques - Dépendance aux énergies fossiles - Mauvaise biodégradabilité #### 🔍 Liste des matières non naturelles : - Polyester - Polyamide - Acrylique - Élasthanne - Viscose - Silicone - … (Ajouter les autres matières) ⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque : - elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et - aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits. Dans ce cas, un avertissement est alors affiché sur la fiche du produit. @ e4950c93:1b99eccd
2025-04-03 14:53:56**Heureu-x-se d’avoir trouvé une information utile sur ce site ?** Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s. --- **En bitcoin** <img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **En euros, dollars, ou toute autre monnaie prise en charge** *Promesses uniquement pour le moment :* <a href="https://liberapay.com/origin-nature/"> <img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200"> </a> --- Contactez-nous si vous souhaitez faire un don avec toute autre cryptomonnaie. --- ### 💡 Un modèle de partage de la valeur La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention. L’autre moitié permet de couvrir les frais de fonctionnement du site.
@ e4950c93:1b99eccd
2025-04-03 14:53:56**Heureu-x-se d’avoir trouvé une information utile sur ce site ?** Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s. --- **En bitcoin** <img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **En euros, dollars, ou toute autre monnaie prise en charge** *Promesses uniquement pour le moment :* <a href="https://liberapay.com/origin-nature/"> <img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200"> </a> --- Contactez-nous si vous souhaitez faire un don avec toute autre cryptomonnaie. --- ### 💡 Un modèle de partage de la valeur La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention. L’autre moitié permet de couvrir les frais de fonctionnement du site. @ 8671a6e5:f88194d1
2025-04-03 14:52:44\~ The person came up to me from behind his merchandise stand and saw my Noderunners pin on my black t-shirt, then looked me dead in the eye and asked : “So… what do you sell?” *This is the eighth long-read in a series of twelve “food for thought” writings on Bitcoin. It was originally meant to be a few chapters in a book, but life’s too short for that.* ## **Define** Let me start by saying there’s no single way to define or explain a “Bitcoin conference.” The experience can vary depending on a few factors: who’s organizing it (a long-time Bitcoiner or someone from traditional finance trying to grasp Bitcoin), where it’s being held (a sunny paradise like Madeira or a gloomy northern French town), and who’s speaking (technical experts or charismatic entertainers or people with little substance). Despite these differences, there’s a shared culture that ties these conferences together: a mix of excitement, frustrations, and inevitable evolution. That’s what I explore. This is just my take, based on what I’ve personally witnessed and what I hear from my surroundings. It’s not meant to be a blanket critique of all Bitcoin conferences as there are plenty I haven’t attended, though I hear about most of them. Even the good ones will evolve into something else over time. So, plan accordingly. A bit of background on my perspective: at some point in my life, I hit a bump in the road that kept me tied to where I live — a bleak corner of Belgium, surrounded by fiat slaves, shitcoiners, and people who spend six hours a day consuming brain-numbing garbage television. Traveling is an exception for me, but for many Bitcoin conference attendees, it’s a ritual, a must-do event. So, I view these events with a mix of fascination and grounded skepticism — something I’ve found lacking in many Bitcoiners. I’ve never been to a Bitcoin conference before 2023, despite receiving plenty of invites over the years. From what I heard and saw in photos from friends who attended (even the real early ones) these events seemed eerily similar to the dull hotel conference rooms I once endured in tech and telecom. I’ve had my fill of lukewarm, watery coffee and lifeless speakers droning on about firewalls. So I skipped that particular honor. Up until around 2018, Bitcoin conferences were a soulless sea of chairs lined up under fluorescent tube lights, draining the life out of attendees—one telecom acronym at a time. Not exactly inviting. Yet, looking back from the perspective of 2025, those were the “pure” days. Back then, people like Roger Ver (before he pivoted to Bitcoin Cash), Andreas Antonopoulos, and encryption specialists spoke to small audiences, explaining Bitcoin in its raw form. But, like any Bitcoiner, I try to improve myself. So, I made the effort to travel, visit other Bitcoiners, and attend Bitcoin conferences. The conferences I attended in 2023/2024 made me a bit wiser ; not necessarily from what was said on stage (with a few lucky exceptions who still try to bring original thoughts). Most of what I learned came from the long queues, the drama, and watching grifters operate in real time and the good characters floating around. So, here’s what I’ve learned. <img src="https://blossom.primal.net/d49fdda9ecb03f04f6c778e5301c67cf2bb15ff3b8647d929cb1755a9f6660a4.png"> **Chain of ticket** I quickly discovered that many Bitcoin conferences have their own “quest for tickets” dynamic, almost like an industry with its own inner circle. It’s a waterfall system: tickets start at lower prices to fill up the venue (usually right after the previous edition). That’s standard practice, both inside and outside of Bitcoin. But what’s strange is seeing organizations that only pop up when a conference needs promotion—somehow securing tickets for themselves and their friends (or for \*making\* friends) while shilling referral links for small discounts to their followers. The real free tickets, though, are a hot topic in many local communities and make all the difference for some attendees. What’s particularly interesting is that most ticket prices can be paid in Bitcoin, adding a layer of calculation to the process. If you paid 230500 sats for your ticket and later see the dollar price fluctuate, say from $180 to $270, or the other way around, by the time the conference starts, you realize you either bought too late or too early.\ It’s better to not have bought at all. Some ticket holders end up paying less (in dollar terms) than others, making it a gamble. As the event date approaches, ticket prices tend to rise—unless you wait until the last minute, when they haven’t sold out, or just pay at the door. It’s a strange feeling knowing that not everyone paid the same amount (and as mentioned, a significant number get in for free) depending on their timing. Many organizations and local community representatives show up primarily to be present; securing free tickets, which function more as a badge of recognition than a necessity.\ It’s similar to how a rock groupie sees backstage access: a status symbol, whether for an autograph or something more. Being seen standing next to big names is a huge deal for some, as they derive their own status from proximity.\ This also reinforces the “rockstar status” that conferences create around certain figures, once they come out to take a selfie with some nice people and young fans, then to quickly disappear back to the ‘whale room’ or backstage. There’s often an entire insider network determining who gets these free tickets. In some cases, it’s naturally tied to the local community, but in others, the professionalism is laughably low. At certain events, you could probably just walk up to the entrance (if there’s even someone checking) and say, “I’m with the organization” to get in for free. It gets even more absurd.\ At a conference near the French-Swiss border, I was probably one of the very few who actually paid for entry. The real spectacle wasn’t in the talk rooms — which remained eerily empty — but in the dining area, where half the town seemed to have shown up just for the free food. Around 200 people queued for a free lunch, while the presentation halls were at best one-third full throughout the day. And beyond the ticket games, there are plenty of ways to slip in unnoticed. Carrying a random piece of equipment and mumbling\ “I need to put this crate in the back” can get you past security. Or you can just wait for the one security guard to get distracted by chatting up a girl or stepping out for a smoke, and you’re in. At one event, I walked in alongside someone carrying crates of wine for the VIP lounge. I blended in perfectly (I paid afterward). So, to sum up: at nearly every conference I’ve been to, a big portion of attendees either walk in for free or hold compensation tickets they got through some connection. Sometimes that connection is uncomfortably close to the organizers. Other times, they just slap an “industry” label on themselves when, in reality, they’re nothing more than a social media bio with a few followers. Local representatives of a podcast, community, influencer network, or fake marketing club also get in for free. And you? The regular guest, you and I are paying for them. There’s no real vetting process; with some organizers, anyone wearing a Bitcoin t-shirt and saying the magic words “I do community building” or “I know the local Bitcoin meetups” gets a free pass. The ones who actually want to learn about Bitcoin — the ones who click the link and pay full price — are the ones covering the costs for everyone else and ultimately making these conferences profitable (or at least break even). The problem? They’re the ones left wondering: “Was it really worth my time and money?” only to never return again most of the time. Because many of the people at these conferences aren’t there to learn. They’re part of the circus. And others? They’re the ones paying for the circus boss, the clowns, and the trapeze artists. At that one conference with the massive free-lunch crowd, I saw one interesting talk. And I had plenty of valuable conversations and observations — conversations I could have just as easily had by visiting that place outside of a conference setting. In the end, I realized the main reason I was there was to support a fellow Bitcoiner giving a presentation. And after that? They disappeared from my life. Because, just like in the fiat world, you’re only as good as your last few hours of usefulness to most people. Which brings me to the next element of Bitcoin conferences...friends **Bitcoin “frens”** This might be the hardest lesson of all: you meet fellow Bitcoiners at these conferences. And some of them? They’re truly special characters. A few even made such a deep connection with not-so-well-traveled-me that I would’ve gladly traveled a full travel day just to spend time working and doing something meaningful together (which I actually did). But most of these connections? They last only a moment. Few survive beyond the conference, mainly because of the vast distances— both in kilometers (or miles) and in the way we live our everyday lives. The Bitcoiners you meet at these events are, for the most part, just regular people trying to make ends meet in the fiat world while saving in Bitcoin. Or they’re chasing the Bitcoin dream or even find a job in the fata morgana of bitcoin jobs. They act like they belong, like a clown acting like he’s going to climb the trapeze. I respect that. But over time, I realized that many of them operate in Bitcoin mode; a kind of facade. Behind that front, that mask, most are just testing the waters to see if they can make it. And most don’t.\ Treating Bitcoin as a lifestyle movement, a career shortcut, or an identity, has its limits. Eventually, the real person breaks through. And you have to face your own instincts and personality.\ I’ve tried to be an acrobat, and ride the lion, make the audience laugh, but I’m still the seal who’s brought back to the cage after he balanced a ball on his nose. The quote “I’m Jack’s wasted life.” came to mind often when standing somewhere at a conference space. Self-doubting people stay self-doubting, owning Bitcoin or not. Emotional wrecks remain emotional wrecks — just with Bitcoin now. And when these masks slip off, you’ll see everything: the greed, the overconfidence, the longing for drama, the addictions, the narcissism, the energy-draining personalities, sleaziness usually with the ones who always say the right oneliners or wear the right Bitcoin merch to blend in. And you can love people for that. Everyone has flaws. Everyone has a price as well. But these Bitcoin “frens” can also hurt you badly. Because as Bitcoiners, we carry hopes. And hopes are like ants on a sidewalk, they’ll eventually get crushed.\ We long to meet people who see the same truth, the same vision of Bitcoin as we do. Some will act like they actually understand and do, they talk the talk for a while, as if they’re parroting a podcast. If you stay in the shadows - like I did for years - you won’t have to deal with these things. If you never try, you’ll never be let down. But you still stay in the imaginary basement, letting yourself down. That’s not the bitcoin style. We router around problems. Even if we stand amidst the problems (like a conference). But if you do? There’s a hefty price to pay — beyond just the money spent. It’s a cost paid in energy, emotions, and social interactions and above all: time. And once in a while, you’ll meet a friend for life. Just be prepared: Bitcoin is a journey that few people you encounter at a conference can take for longer than four years, or even four hours of conversation actually. And then, after navigating the social maze of Bitcoin conferences —the connections, the masks, the fleeting friendships, the smell of weed and regret — you find yourself facing an even greater challenge: the queue at a coffee stall. <img src="https://blossom.primal.net/26f00a14b1ff12ea82635f1fd659900a7a836d37591556a31fda91d8210dcff0.png"> ## ## \ The Soviet LN Queue It’s one of the most fascinating and frustrating aspects of every conference: the insanely long lines. Whether it’s for the toilets, a coffee booth, or some niche merchandise stall, you’ll see Bitcoiners waiting like it’s 1963 after a Soviet state bakery just got fresh deliveries. waiting for coffee Seriously, aren’t we supposed to be the pinnacle of free-market efficiency? Instead, we’ve somehow perfected the art of the long food lines. I remember people waiting in line for like 35 minutes to order a cappuccino! The usual culprit? A mix of payment chaos and the Bitcoin Orangepill mental issues in action. A large portion insists on using Lightning (as in "their preferred lighting wallet"), which would be fine except they’re fumbling with some exotic, half-working wallet because using something that’s actually fast might get them sneered at for being “custodial.” On top of that, vendors are juggling card payments, cash, various Lightning POS systems, and even the occasional cutting edge dudes trying to pay with an Apple Watch or worse, some newly released Lightning-enabled gadget that doesn’t work yet. And when it does work, it requires so much attention and Instagram footage that it takes five minutes just to hand someone a coffee while the guy pays with a lighting NFC ring on his finger, something you can't use ànywhere else ever. It’s cool. But not to anyone else than you. So, here’s a tip for the regular people, the rats that pay for all of this : sneak out. Then you find a small, locally owned café outside the conference, pay them in cash, and actually enjoy your food in a few seconds or minutes. If (and only if) they accept Bitcoin, great! Tip them well. Otherwise, just relax and have a conversation with a local, all the while inside the conference venue there are Bitcoiners filming each other struggling to make a payment with the latest Lightning-enabled NFC card or making the staff uneasy. Meanwhile, some poor 22-year-old café worker is trapped in an unsolicited podcast participation: “Wait, you accept tips in Wallet of Satoshi? Who told you that? I’ll explain it to you!” Or worse: “Hold on, I just need to do a quick swap… It’s an on-chain transaction, the last block was 19 minutes ago, can’t be long now… wait… umm… do you take VISA?” At this point, ordering a simple drink at a Bitcoin conference has become an unnecessarily complex, ego-driven performance. With long queues as a direct result. And don’t get me started on the story when 30+ bitcoiners walked in to a Portuguese restaurant without a reservation, and they all wanted to pay with different payment methods. It was like the Vietnam war. **Solution:** A tip for conference organizers and their catering : pick one Bitcoin point of sales system, set clear guidelines, and make everyone stick to them. Instruct people to adhere to the following : Pay with a (bank) card, cash, or Lightning and PLEASE decide beforehand which method you’re using before ordering your stuff! We prefer lighting. If you’re using Lightning, have enough balance on you wallet or get lost. Use a compatible wallet. (Provide a tested “approved” list and train staff properly. Users who use other stuff get their order “cancelled” at the first sign of trouble. Your app‘s not scanning, or not compatible, or it has some technical mumbo-jumbo going on to your vpn LN node at home 2000 km away? Please get real and pay with a bank card or something. No filming, duck-facing (like it's 2017) or stupid selfies with your payment. It’s been done a thousand times by now. There are people in line, waiting behind you, they want to order as well, while you have your little ego trip or marketing moment. Move on please! “Our staff knows how bitcoin payments work, you don’t need to #orangesplain it to anyone.” We don’t care about your 200th LN app or the latest “but… this one is faster” thingy. Order your drinks, pay and get out of the way please. Bitcoin fixes many things. But it hasn’t quite fixed this yet. The bitcoin conference axiom Going to a conference, versus keeping your bitcoin in your wallet is a tough choice for many. If you pay nothing for tickets and lodging, while enjoying free meals and cocktails, your opportunity cost drops close to zero —yet your networking and social impact are maximized while you can also do business. That’s ideal. At least, for you. In such case, Bitcoin may only "win" over an extended timeline, but for you, it's essentially a free ride. You incur no real opportunity costs. You drink their milkshake. On the other hand, if you’re a regular attendee, you pay full price: the ticket, overpriced drinks and food from the stands (losing even more if you generously pay for coffee in sats), plus extras like t-shirts and books (which you’ll never read). Your milkshake gets taken—at least half of it. If you’re lucky, you might spend an evening in town with the event’s "stars"—those occasional luminaries who briefly grace the normies with their presence for a drink. Some can’t even hold their liquor. Year after year, the same 10 to 15 speakers or panelists appear, funded by your dime, traveling the world and enjoying the perks—some even cultivating fan bases and hosting exclusive parties. The real opportunity cost hits hardest for regular attendees who come to learn, shelling out significant money while accumulating their fourth hardware wallet or yet another orange-themed t-shirt. They might even squeeze in a selfie with a former sportswear model turned Bitcoiner. For normies (as they’re often called), the financial and social scales rarely tip in their favor. **Calculating the conference opportunity cost** To determine the opportunity cost of attending a conference instead of investing in Bitcoin, over time follow these steps: 1. Calculate your total conference expenses, including tickets, travel, food, drinks, and lodging (merchandise and donations). 2. Estimate Bitcoin’s percentage gain over the conference period and the following year(s). (in order to not make you cry, I suggest nog going over 5 years) 3. Multiply your total conference cost by this percentage to determine the potential Bitcoin profit you forgo. 4. Assign a dollar value to the networking or business opportunities you expect to gain from the conference (if you’re not just in it for the laughs, meeting high-class consultants, friendships, self-proclaimed social media Bitcoiners, or the occasional gyrating on one of the musicians/artists/food stall staff members). 5. Subtract this “networking” value from the missed Bitcoin profit to find your net opportunity cost (this is rather personal,… with me it’s zero, but for someone selling t-shirts it’s probably much more). If the result is negative over the chosen timeframe, the conference was financially worthwhile for you. If positive, holding or buying Bitcoin was the smarter move. Unless you’re a recognized speaker in this traveling circus, your opportunity cost will likely be positive — meaning all the others lose hard money, while fumbling with your Lightning wallet. The Conference Opportunity Cost Formula Let: CT = Total conference ticket & entrance cost (in dollars) CR = Total related conference costs (travel, lodging, food, etc.) C = CT + CR (Total cost) G = Bitcoin’s % gain per year (as a decimal, e.g., 5% = 0.05) N = Estimated fiat value of networking/business opportunities and knowledge gained. ### OC = (C × G) − N Where: OC (Opportunity Cost) < 0 → The conference was worth attending. OC (Opportunity Cost) > 0 → Holding/buying Bitcoin was the better move. Some example calculations (I've left out examples before 2020, I don't want people crying or waking up at night thinking "Why did I go to Amsterdam in 2014?!") example : Conference in April 2024 Entrance: $200 Lodging, t-shirt, and travel: $900 Bitcoin's estimated gain: 23% (0.23) No business / knowledge value gained OC = (200 + 900) × 0.23 - 0 - $253 OC (Bitcoin would have been the better choice.) Conference in April 2020 (adjusted for historical Bitcoin growth) Entrance: $175 Lodging and travel: $700 Bitcoin's estimated gain: 1089% (10.89) No business / knowledge value gained OC = (175 + 700) × 10.89 - 0 OC = +$9,529 (Massive missed gains — Bitcoin was the clear winner. \-- So the first lesson in bitcoin should be: Only attend conferences if you get paid to do so and get a free ticket and free lodging, which kind of would kill that whole industry to begin with. ### Energizing At first, it’s energizing to meet like-minded bitcoiners, but after a while, you realize that a big chunk of them are just trying to sell you something or aren’t really bitcoin-focused at all. And some of them are just looking for their next way to kill time and boredom. The drama that comes with attending these conference and the personal interaction can get pretty intense at times, since expectations often don’t match the personalities. Before you know, you’re walking around at night through some bad part of a town, while crying your eyes out because you thought you found your soulmate. Future pure industry conferences will suffer less from this drama, because everyone there has the same goal — pushing their company or product— while the “other” grassroots conferences are more of a meeting spot for bitcoiners of all types and perspectives, bringing the usual drama and mess that comes with human interactions. Current conferences are a mix of both usually. I think the current era of bitcoin conferences is coming to an end. Soon, probably by the end of 2025, we’ll see a clear split between industry-driven and human-driven (grassroots) smaller conferences, and it’ll be really important to keep these two separate. I even had the idea to launch a sort of conference where there wouldn’t be any industry speakers or companies present. Just bitcoiners gathering at a certain place at a specific week and having a good time. I called it “club Sat” And you could just go there, and meet other bitcoiners, while acting there was a big venue and speakers,… but there aren’t any. Would be refreshing. No struggle for tickets, no backstage stuff, no boring talks and presentation,… just the surroundings and the drama lever you want and probably like. ### On stage The podium is usually left for the known names. Not every conference is like that, but most of them need these names, badly. These names know each other, they encounter one another in VIP rooms and “the industry” a lot of times anyway. The same people you see in the bitcoin news, the same people having a cult following, and the very same people traveling, staying and drinking for free while spreading the same bitcoin wisdoms will be invited over and over again. Or… they go rock around as they’re usually so bored they had to start a rock band to entertain themselves. Which is rather entertaining if you’re following up on who does what, but in the end it’s largely just for their own amusement and it shows. I get that. I would do the same. It’s fun and all. It’s just a bit sad that there are only a small group of top-layer speakers, and then the sub-top that usually has more to say, or gets little opportunity. The reason for that is simple: the “normies” who pay in full for tickets, come there for the “big” names. They don’t know that much about bitcoin usually, so they’re not waiting on some unknown dude explaining something about an obscure niche subject. A debate can help remedie this, to mix it in with some lesser known names, but I have the feeling the current “line-up” of bitcoin conferences feels like a rock festival in 2025 putting the Stone temple pilots or Creed on the card. Yes, they’ll attract an audience and do their playset well,… but it’s not exactly the pinnacle of the music industry at the moment, neither is Madonna by the way :) ## Promoting anything The people organizing these events usually aren’t Bitcoiners either — they’re promoters (few exceptions though). <img src="https://blossom.primal.net/f478bf793b2048a51a15ceab5b8384abdb8d00c6d7c3cdd16731f5379cc1417d.png"> They don’t care if they organize a symposium about a newly discovered STD, A three-day cheese tasting event, a Star Trek convention, or a Lucha Libre wrestling tournament featuring El HODLador, as long as they can sell tickets and make money from merchandise they're good. The last thing on the mind with some of them will be helping bitcoin adoption. There will be a time (soon) where people that know bitcoin, known bitcoiners and know how to organize events get their act together. It will be different than the early days, and it will be different than the boring going-through-the-motions conferences we have now. There shall be fun, social gatherings, life, excitement and culture, and not the “what do you sell?” atmosphere, neither the “this old dude on stage again”? That’s why they’ll slap any semi-famous name on the poster to pull in a crowd - could be a washed-up Mexican wrestling star with strange legal issues, the cheese-tasting equivalent of Usain Bolt, or your neighborhood Bitcoin old-timer with a beard and a "best selling author" label. It’s also why most of these conferences end up being more about shitcoins than anything else. And even if they're for the most part about bitcoin, the venue is usually infested with marketing budgets, useless organizations that wanted complimentary tickets (some of them do only one thing: popping up when a conference is nearby and then they’re gone again) ... along with some hawking consultant types you never see anywhere else. They'll occasionally pay people but usually in fiat, or if you're a bigger name, you might get other deals. For artists or staff, it's all in fiat from what I heard. Pure Bitcoin conferences, also rely on these big names. Whether it’s a well-known Bitcoiner, a CEO, president, or someone with real reveling knowledge to share with the audience (though that last type is getting rare). ### **Looking for love in all the wrong places** \ Let’s also address the fair share of “orange diggers” at Bitcoin conferences—because yes, they exist. And no, let’s not single out one particular gender here. Some people treat a Bitcoin conference like a live-action dating app mixed with a financial vetting process for potential partners. It’s essentially an opportunity to inspect and assess the grab bag of fintech, crypto, and Bitcoin folks in real life. And if you think this is exaggerated, just attend a few conferences—three is enough. You’ll start noticing the same people popping up, seemingly without any real Bitcoin knowledge, but with a very strong interest in dining, chatting, and generally being around—as long as you look and play the part. I can only imagine how dialed-up this effect must be at a shitcoin conference — probably like flies on a cowpie. The trick is, in Bitcoin, these people try to blend in. Some even tag along with real Bitcoiners, while others just crash the party and try to get noticed. Their actual interest in Bitcoin? Close to zero. Their main target? Your wallet, or some fantasy thing about getting to know someone out of the ordinary. And that’s a shame for the people who genuinely care about Bitcoin, who want to network, or who simply are looking for like-minded people. They often find themselves competing for attention with those who’ve turned “being noticed” into a sport, while the rest just wander around, lost in the shuffle. Talk to the quiet ones. Certainly if they look like they belong in a antiques shop. My advice: Talk to people and be genuine. If you don’t know much about Bitcoin, that’s fine - nobody expects you to be a walking whitepaper and on top of that, most people you'll encounter don't know that much either. It’s bitcoin: we’re all rather average people that hold an extraordinary asset. Just don’t be "that orange digger" looking for a partner with a loaded bag of bitcoin. Because in the end, what’s the prize you win? You don’t know who’s under the mask. You don’t even know who’s under your own mask. Finding a man or woman at a place where half the people are laser-focused on financial sovereignty, and the other half are busy arguing about seed phrase storage, UTXO management, and why your Lightning wallet sucks? But good luck with that. The judge of character usually comes when they find the next shiny object or ditched you standing in the rain at the entrance of a restaurant while dealing with a lightning watchtower or a funny cigarette or whatever. If you’re truly looking for love, maybe stick to going to a normal bar. If you’re here to learn, connect, and be part of something of a grassroots movement, then be real yourself. I've seen some rather nasty examples of people at Bitcoin conferences—of all kinds. And I've also seen some really cool examples of truly awesome people. This led me to believe that Bitcoin conferences simply let you meet… people, just dialed up a bit. Future If you encounter rotten people, they’ll usually be even more rotten than in the fiat world. If you meet really cool people, they’ll be even more awesome than the cool people in the fiat world. Our volatility is our freedom. So, I guess it’s normal. Doesn’t make it any easier, though. Bitcoin sees through bullshit, and so do Bitcoiners (even if it takes 21,000 blocks) Pretty soon, I reckon we’ll see conferences fork into two camps: grass roots, and the “industry” level ones. (human / corporate) I guess I’ll only attend the human part, for sure, but I can’t help but booking myself a single room in a hotel in a nice area in that case, so I don’t have to deal with class of 2022 hippies sharing referral links to their middleman service while asking me for a lighter 3 times in a row. The chances for me of meeting cool bitcoiners in a nearby cocktail bar are a lot higher. In the meanwhile, I’ll look forward and see how the bitcoin conferences will evolve, fork in two “styles”. One corporate and one underground. Maybe there will be one more genre just for the fun of it. I’ll stay away, as I don’t like this current mix of industry gigs and having the insiders and “the rest” of us all mingled together clamoring for tickets, attention and coffee. The game is rigged. Staying at home is the better option (for now). written by AVB If you like : [tip here](https://coinos.io/allesvoorbitcoin/receive)
@ 8671a6e5:f88194d1
2025-04-03 14:52:44\~ The person came up to me from behind his merchandise stand and saw my Noderunners pin on my black t-shirt, then looked me dead in the eye and asked : “So… what do you sell?” *This is the eighth long-read in a series of twelve “food for thought” writings on Bitcoin. It was originally meant to be a few chapters in a book, but life’s too short for that.* ## **Define** Let me start by saying there’s no single way to define or explain a “Bitcoin conference.” The experience can vary depending on a few factors: who’s organizing it (a long-time Bitcoiner or someone from traditional finance trying to grasp Bitcoin), where it’s being held (a sunny paradise like Madeira or a gloomy northern French town), and who’s speaking (technical experts or charismatic entertainers or people with little substance). Despite these differences, there’s a shared culture that ties these conferences together: a mix of excitement, frustrations, and inevitable evolution. That’s what I explore. This is just my take, based on what I’ve personally witnessed and what I hear from my surroundings. It’s not meant to be a blanket critique of all Bitcoin conferences as there are plenty I haven’t attended, though I hear about most of them. Even the good ones will evolve into something else over time. So, plan accordingly. A bit of background on my perspective: at some point in my life, I hit a bump in the road that kept me tied to where I live — a bleak corner of Belgium, surrounded by fiat slaves, shitcoiners, and people who spend six hours a day consuming brain-numbing garbage television. Traveling is an exception for me, but for many Bitcoin conference attendees, it’s a ritual, a must-do event. So, I view these events with a mix of fascination and grounded skepticism — something I’ve found lacking in many Bitcoiners. I’ve never been to a Bitcoin conference before 2023, despite receiving plenty of invites over the years. From what I heard and saw in photos from friends who attended (even the real early ones) these events seemed eerily similar to the dull hotel conference rooms I once endured in tech and telecom. I’ve had my fill of lukewarm, watery coffee and lifeless speakers droning on about firewalls. So I skipped that particular honor. Up until around 2018, Bitcoin conferences were a soulless sea of chairs lined up under fluorescent tube lights, draining the life out of attendees—one telecom acronym at a time. Not exactly inviting. Yet, looking back from the perspective of 2025, those were the “pure” days. Back then, people like Roger Ver (before he pivoted to Bitcoin Cash), Andreas Antonopoulos, and encryption specialists spoke to small audiences, explaining Bitcoin in its raw form. But, like any Bitcoiner, I try to improve myself. So, I made the effort to travel, visit other Bitcoiners, and attend Bitcoin conferences. The conferences I attended in 2023/2024 made me a bit wiser ; not necessarily from what was said on stage (with a few lucky exceptions who still try to bring original thoughts). Most of what I learned came from the long queues, the drama, and watching grifters operate in real time and the good characters floating around. So, here’s what I’ve learned. <img src="https://blossom.primal.net/d49fdda9ecb03f04f6c778e5301c67cf2bb15ff3b8647d929cb1755a9f6660a4.png"> **Chain of ticket** I quickly discovered that many Bitcoin conferences have their own “quest for tickets” dynamic, almost like an industry with its own inner circle. It’s a waterfall system: tickets start at lower prices to fill up the venue (usually right after the previous edition). That’s standard practice, both inside and outside of Bitcoin. But what’s strange is seeing organizations that only pop up when a conference needs promotion—somehow securing tickets for themselves and their friends (or for \*making\* friends) while shilling referral links for small discounts to their followers. The real free tickets, though, are a hot topic in many local communities and make all the difference for some attendees. What’s particularly interesting is that most ticket prices can be paid in Bitcoin, adding a layer of calculation to the process. If you paid 230500 sats for your ticket and later see the dollar price fluctuate, say from $180 to $270, or the other way around, by the time the conference starts, you realize you either bought too late or too early.\ It’s better to not have bought at all. Some ticket holders end up paying less (in dollar terms) than others, making it a gamble. As the event date approaches, ticket prices tend to rise—unless you wait until the last minute, when they haven’t sold out, or just pay at the door. It’s a strange feeling knowing that not everyone paid the same amount (and as mentioned, a significant number get in for free) depending on their timing. Many organizations and local community representatives show up primarily to be present; securing free tickets, which function more as a badge of recognition than a necessity.\ It’s similar to how a rock groupie sees backstage access: a status symbol, whether for an autograph or something more. Being seen standing next to big names is a huge deal for some, as they derive their own status from proximity.\ This also reinforces the “rockstar status” that conferences create around certain figures, once they come out to take a selfie with some nice people and young fans, then to quickly disappear back to the ‘whale room’ or backstage. There’s often an entire insider network determining who gets these free tickets. In some cases, it’s naturally tied to the local community, but in others, the professionalism is laughably low. At certain events, you could probably just walk up to the entrance (if there’s even someone checking) and say, “I’m with the organization” to get in for free. It gets even more absurd.\ At a conference near the French-Swiss border, I was probably one of the very few who actually paid for entry. The real spectacle wasn’t in the talk rooms — which remained eerily empty — but in the dining area, where half the town seemed to have shown up just for the free food. Around 200 people queued for a free lunch, while the presentation halls were at best one-third full throughout the day. And beyond the ticket games, there are plenty of ways to slip in unnoticed. Carrying a random piece of equipment and mumbling\ “I need to put this crate in the back” can get you past security. Or you can just wait for the one security guard to get distracted by chatting up a girl or stepping out for a smoke, and you’re in. At one event, I walked in alongside someone carrying crates of wine for the VIP lounge. I blended in perfectly (I paid afterward). So, to sum up: at nearly every conference I’ve been to, a big portion of attendees either walk in for free or hold compensation tickets they got through some connection. Sometimes that connection is uncomfortably close to the organizers. Other times, they just slap an “industry” label on themselves when, in reality, they’re nothing more than a social media bio with a few followers. Local representatives of a podcast, community, influencer network, or fake marketing club also get in for free. And you? The regular guest, you and I are paying for them. There’s no real vetting process; with some organizers, anyone wearing a Bitcoin t-shirt and saying the magic words “I do community building” or “I know the local Bitcoin meetups” gets a free pass. The ones who actually want to learn about Bitcoin — the ones who click the link and pay full price — are the ones covering the costs for everyone else and ultimately making these conferences profitable (or at least break even). The problem? They’re the ones left wondering: “Was it really worth my time and money?” only to never return again most of the time. Because many of the people at these conferences aren’t there to learn. They’re part of the circus. And others? They’re the ones paying for the circus boss, the clowns, and the trapeze artists. At that one conference with the massive free-lunch crowd, I saw one interesting talk. And I had plenty of valuable conversations and observations — conversations I could have just as easily had by visiting that place outside of a conference setting. In the end, I realized the main reason I was there was to support a fellow Bitcoiner giving a presentation. And after that? They disappeared from my life. Because, just like in the fiat world, you’re only as good as your last few hours of usefulness to most people. Which brings me to the next element of Bitcoin conferences...friends **Bitcoin “frens”** This might be the hardest lesson of all: you meet fellow Bitcoiners at these conferences. And some of them? They’re truly special characters. A few even made such a deep connection with not-so-well-traveled-me that I would’ve gladly traveled a full travel day just to spend time working and doing something meaningful together (which I actually did). But most of these connections? They last only a moment. Few survive beyond the conference, mainly because of the vast distances— both in kilometers (or miles) and in the way we live our everyday lives. The Bitcoiners you meet at these events are, for the most part, just regular people trying to make ends meet in the fiat world while saving in Bitcoin. Or they’re chasing the Bitcoin dream or even find a job in the fata morgana of bitcoin jobs. They act like they belong, like a clown acting like he’s going to climb the trapeze. I respect that. But over time, I realized that many of them operate in Bitcoin mode; a kind of facade. Behind that front, that mask, most are just testing the waters to see if they can make it. And most don’t.\ Treating Bitcoin as a lifestyle movement, a career shortcut, or an identity, has its limits. Eventually, the real person breaks through. And you have to face your own instincts and personality.\ I’ve tried to be an acrobat, and ride the lion, make the audience laugh, but I’m still the seal who’s brought back to the cage after he balanced a ball on his nose. The quote “I’m Jack’s wasted life.” came to mind often when standing somewhere at a conference space. Self-doubting people stay self-doubting, owning Bitcoin or not. Emotional wrecks remain emotional wrecks — just with Bitcoin now. And when these masks slip off, you’ll see everything: the greed, the overconfidence, the longing for drama, the addictions, the narcissism, the energy-draining personalities, sleaziness usually with the ones who always say the right oneliners or wear the right Bitcoin merch to blend in. And you can love people for that. Everyone has flaws. Everyone has a price as well. But these Bitcoin “frens” can also hurt you badly. Because as Bitcoiners, we carry hopes. And hopes are like ants on a sidewalk, they’ll eventually get crushed.\ We long to meet people who see the same truth, the same vision of Bitcoin as we do. Some will act like they actually understand and do, they talk the talk for a while, as if they’re parroting a podcast. If you stay in the shadows - like I did for years - you won’t have to deal with these things. If you never try, you’ll never be let down. But you still stay in the imaginary basement, letting yourself down. That’s not the bitcoin style. We router around problems. Even if we stand amidst the problems (like a conference). But if you do? There’s a hefty price to pay — beyond just the money spent. It’s a cost paid in energy, emotions, and social interactions and above all: time. And once in a while, you’ll meet a friend for life. Just be prepared: Bitcoin is a journey that few people you encounter at a conference can take for longer than four years, or even four hours of conversation actually. And then, after navigating the social maze of Bitcoin conferences —the connections, the masks, the fleeting friendships, the smell of weed and regret — you find yourself facing an even greater challenge: the queue at a coffee stall. <img src="https://blossom.primal.net/26f00a14b1ff12ea82635f1fd659900a7a836d37591556a31fda91d8210dcff0.png"> ## ## \ The Soviet LN Queue It’s one of the most fascinating and frustrating aspects of every conference: the insanely long lines. Whether it’s for the toilets, a coffee booth, or some niche merchandise stall, you’ll see Bitcoiners waiting like it’s 1963 after a Soviet state bakery just got fresh deliveries. waiting for coffee Seriously, aren’t we supposed to be the pinnacle of free-market efficiency? Instead, we’ve somehow perfected the art of the long food lines. I remember people waiting in line for like 35 minutes to order a cappuccino! The usual culprit? A mix of payment chaos and the Bitcoin Orangepill mental issues in action. A large portion insists on using Lightning (as in "their preferred lighting wallet"), which would be fine except they’re fumbling with some exotic, half-working wallet because using something that’s actually fast might get them sneered at for being “custodial.” On top of that, vendors are juggling card payments, cash, various Lightning POS systems, and even the occasional cutting edge dudes trying to pay with an Apple Watch or worse, some newly released Lightning-enabled gadget that doesn’t work yet. And when it does work, it requires so much attention and Instagram footage that it takes five minutes just to hand someone a coffee while the guy pays with a lighting NFC ring on his finger, something you can't use ànywhere else ever. It’s cool. But not to anyone else than you. So, here’s a tip for the regular people, the rats that pay for all of this : sneak out. Then you find a small, locally owned café outside the conference, pay them in cash, and actually enjoy your food in a few seconds or minutes. If (and only if) they accept Bitcoin, great! Tip them well. Otherwise, just relax and have a conversation with a local, all the while inside the conference venue there are Bitcoiners filming each other struggling to make a payment with the latest Lightning-enabled NFC card or making the staff uneasy. Meanwhile, some poor 22-year-old café worker is trapped in an unsolicited podcast participation: “Wait, you accept tips in Wallet of Satoshi? Who told you that? I’ll explain it to you!” Or worse: “Hold on, I just need to do a quick swap… It’s an on-chain transaction, the last block was 19 minutes ago, can’t be long now… wait… umm… do you take VISA?” At this point, ordering a simple drink at a Bitcoin conference has become an unnecessarily complex, ego-driven performance. With long queues as a direct result. And don’t get me started on the story when 30+ bitcoiners walked in to a Portuguese restaurant without a reservation, and they all wanted to pay with different payment methods. It was like the Vietnam war. **Solution:** A tip for conference organizers and their catering : pick one Bitcoin point of sales system, set clear guidelines, and make everyone stick to them. Instruct people to adhere to the following : Pay with a (bank) card, cash, or Lightning and PLEASE decide beforehand which method you’re using before ordering your stuff! We prefer lighting. If you’re using Lightning, have enough balance on you wallet or get lost. Use a compatible wallet. (Provide a tested “approved” list and train staff properly. Users who use other stuff get their order “cancelled” at the first sign of trouble. Your app‘s not scanning, or not compatible, or it has some technical mumbo-jumbo going on to your vpn LN node at home 2000 km away? Please get real and pay with a bank card or something. No filming, duck-facing (like it's 2017) or stupid selfies with your payment. It’s been done a thousand times by now. There are people in line, waiting behind you, they want to order as well, while you have your little ego trip or marketing moment. Move on please! “Our staff knows how bitcoin payments work, you don’t need to #orangesplain it to anyone.” We don’t care about your 200th LN app or the latest “but… this one is faster” thingy. Order your drinks, pay and get out of the way please. Bitcoin fixes many things. But it hasn’t quite fixed this yet. The bitcoin conference axiom Going to a conference, versus keeping your bitcoin in your wallet is a tough choice for many. If you pay nothing for tickets and lodging, while enjoying free meals and cocktails, your opportunity cost drops close to zero —yet your networking and social impact are maximized while you can also do business. That’s ideal. At least, for you. In such case, Bitcoin may only "win" over an extended timeline, but for you, it's essentially a free ride. You incur no real opportunity costs. You drink their milkshake. On the other hand, if you’re a regular attendee, you pay full price: the ticket, overpriced drinks and food from the stands (losing even more if you generously pay for coffee in sats), plus extras like t-shirts and books (which you’ll never read). Your milkshake gets taken—at least half of it. If you’re lucky, you might spend an evening in town with the event’s "stars"—those occasional luminaries who briefly grace the normies with their presence for a drink. Some can’t even hold their liquor. Year after year, the same 10 to 15 speakers or panelists appear, funded by your dime, traveling the world and enjoying the perks—some even cultivating fan bases and hosting exclusive parties. The real opportunity cost hits hardest for regular attendees who come to learn, shelling out significant money while accumulating their fourth hardware wallet or yet another orange-themed t-shirt. They might even squeeze in a selfie with a former sportswear model turned Bitcoiner. For normies (as they’re often called), the financial and social scales rarely tip in their favor. **Calculating the conference opportunity cost** To determine the opportunity cost of attending a conference instead of investing in Bitcoin, over time follow these steps: 1. Calculate your total conference expenses, including tickets, travel, food, drinks, and lodging (merchandise and donations). 2. Estimate Bitcoin’s percentage gain over the conference period and the following year(s). (in order to not make you cry, I suggest nog going over 5 years) 3. Multiply your total conference cost by this percentage to determine the potential Bitcoin profit you forgo. 4. Assign a dollar value to the networking or business opportunities you expect to gain from the conference (if you’re not just in it for the laughs, meeting high-class consultants, friendships, self-proclaimed social media Bitcoiners, or the occasional gyrating on one of the musicians/artists/food stall staff members). 5. Subtract this “networking” value from the missed Bitcoin profit to find your net opportunity cost (this is rather personal,… with me it’s zero, but for someone selling t-shirts it’s probably much more). If the result is negative over the chosen timeframe, the conference was financially worthwhile for you. If positive, holding or buying Bitcoin was the smarter move. Unless you’re a recognized speaker in this traveling circus, your opportunity cost will likely be positive — meaning all the others lose hard money, while fumbling with your Lightning wallet. The Conference Opportunity Cost Formula Let: CT = Total conference ticket & entrance cost (in dollars) CR = Total related conference costs (travel, lodging, food, etc.) C = CT + CR (Total cost) G = Bitcoin’s % gain per year (as a decimal, e.g., 5% = 0.05) N = Estimated fiat value of networking/business opportunities and knowledge gained. ### OC = (C × G) − N Where: OC (Opportunity Cost) < 0 → The conference was worth attending. OC (Opportunity Cost) > 0 → Holding/buying Bitcoin was the better move. Some example calculations (I've left out examples before 2020, I don't want people crying or waking up at night thinking "Why did I go to Amsterdam in 2014?!") example : Conference in April 2024 Entrance: $200 Lodging, t-shirt, and travel: $900 Bitcoin's estimated gain: 23% (0.23) No business / knowledge value gained OC = (200 + 900) × 0.23 - 0 - $253 OC (Bitcoin would have been the better choice.) Conference in April 2020 (adjusted for historical Bitcoin growth) Entrance: $175 Lodging and travel: $700 Bitcoin's estimated gain: 1089% (10.89) No business / knowledge value gained OC = (175 + 700) × 10.89 - 0 OC = +$9,529 (Massive missed gains — Bitcoin was the clear winner. \-- So the first lesson in bitcoin should be: Only attend conferences if you get paid to do so and get a free ticket and free lodging, which kind of would kill that whole industry to begin with. ### Energizing At first, it’s energizing to meet like-minded bitcoiners, but after a while, you realize that a big chunk of them are just trying to sell you something or aren’t really bitcoin-focused at all. And some of them are just looking for their next way to kill time and boredom. The drama that comes with attending these conference and the personal interaction can get pretty intense at times, since expectations often don’t match the personalities. Before you know, you’re walking around at night through some bad part of a town, while crying your eyes out because you thought you found your soulmate. Future pure industry conferences will suffer less from this drama, because everyone there has the same goal — pushing their company or product— while the “other” grassroots conferences are more of a meeting spot for bitcoiners of all types and perspectives, bringing the usual drama and mess that comes with human interactions. Current conferences are a mix of both usually. I think the current era of bitcoin conferences is coming to an end. Soon, probably by the end of 2025, we’ll see a clear split between industry-driven and human-driven (grassroots) smaller conferences, and it’ll be really important to keep these two separate. I even had the idea to launch a sort of conference where there wouldn’t be any industry speakers or companies present. Just bitcoiners gathering at a certain place at a specific week and having a good time. I called it “club Sat” And you could just go there, and meet other bitcoiners, while acting there was a big venue and speakers,… but there aren’t any. Would be refreshing. No struggle for tickets, no backstage stuff, no boring talks and presentation,… just the surroundings and the drama lever you want and probably like. ### On stage The podium is usually left for the known names. Not every conference is like that, but most of them need these names, badly. These names know each other, they encounter one another in VIP rooms and “the industry” a lot of times anyway. The same people you see in the bitcoin news, the same people having a cult following, and the very same people traveling, staying and drinking for free while spreading the same bitcoin wisdoms will be invited over and over again. Or… they go rock around as they’re usually so bored they had to start a rock band to entertain themselves. Which is rather entertaining if you’re following up on who does what, but in the end it’s largely just for their own amusement and it shows. I get that. I would do the same. It’s fun and all. It’s just a bit sad that there are only a small group of top-layer speakers, and then the sub-top that usually has more to say, or gets little opportunity. The reason for that is simple: the “normies” who pay in full for tickets, come there for the “big” names. They don’t know that much about bitcoin usually, so they’re not waiting on some unknown dude explaining something about an obscure niche subject. A debate can help remedie this, to mix it in with some lesser known names, but I have the feeling the current “line-up” of bitcoin conferences feels like a rock festival in 2025 putting the Stone temple pilots or Creed on the card. Yes, they’ll attract an audience and do their playset well,… but it’s not exactly the pinnacle of the music industry at the moment, neither is Madonna by the way :) ## Promoting anything The people organizing these events usually aren’t Bitcoiners either — they’re promoters (few exceptions though). <img src="https://blossom.primal.net/f478bf793b2048a51a15ceab5b8384abdb8d00c6d7c3cdd16731f5379cc1417d.png"> They don’t care if they organize a symposium about a newly discovered STD, A three-day cheese tasting event, a Star Trek convention, or a Lucha Libre wrestling tournament featuring El HODLador, as long as they can sell tickets and make money from merchandise they're good. The last thing on the mind with some of them will be helping bitcoin adoption. There will be a time (soon) where people that know bitcoin, known bitcoiners and know how to organize events get their act together. It will be different than the early days, and it will be different than the boring going-through-the-motions conferences we have now. There shall be fun, social gatherings, life, excitement and culture, and not the “what do you sell?” atmosphere, neither the “this old dude on stage again”? That’s why they’ll slap any semi-famous name on the poster to pull in a crowd - could be a washed-up Mexican wrestling star with strange legal issues, the cheese-tasting equivalent of Usain Bolt, or your neighborhood Bitcoin old-timer with a beard and a "best selling author" label. It’s also why most of these conferences end up being more about shitcoins than anything else. And even if they're for the most part about bitcoin, the venue is usually infested with marketing budgets, useless organizations that wanted complimentary tickets (some of them do only one thing: popping up when a conference is nearby and then they’re gone again) ... along with some hawking consultant types you never see anywhere else. They'll occasionally pay people but usually in fiat, or if you're a bigger name, you might get other deals. For artists or staff, it's all in fiat from what I heard. Pure Bitcoin conferences, also rely on these big names. Whether it’s a well-known Bitcoiner, a CEO, president, or someone with real reveling knowledge to share with the audience (though that last type is getting rare). ### **Looking for love in all the wrong places** \ Let’s also address the fair share of “orange diggers” at Bitcoin conferences—because yes, they exist. And no, let’s not single out one particular gender here. Some people treat a Bitcoin conference like a live-action dating app mixed with a financial vetting process for potential partners. It’s essentially an opportunity to inspect and assess the grab bag of fintech, crypto, and Bitcoin folks in real life. And if you think this is exaggerated, just attend a few conferences—three is enough. You’ll start noticing the same people popping up, seemingly without any real Bitcoin knowledge, but with a very strong interest in dining, chatting, and generally being around—as long as you look and play the part. I can only imagine how dialed-up this effect must be at a shitcoin conference — probably like flies on a cowpie. The trick is, in Bitcoin, these people try to blend in. Some even tag along with real Bitcoiners, while others just crash the party and try to get noticed. Their actual interest in Bitcoin? Close to zero. Their main target? Your wallet, or some fantasy thing about getting to know someone out of the ordinary. And that’s a shame for the people who genuinely care about Bitcoin, who want to network, or who simply are looking for like-minded people. They often find themselves competing for attention with those who’ve turned “being noticed” into a sport, while the rest just wander around, lost in the shuffle. Talk to the quiet ones. Certainly if they look like they belong in a antiques shop. My advice: Talk to people and be genuine. If you don’t know much about Bitcoin, that’s fine - nobody expects you to be a walking whitepaper and on top of that, most people you'll encounter don't know that much either. It’s bitcoin: we’re all rather average people that hold an extraordinary asset. Just don’t be "that orange digger" looking for a partner with a loaded bag of bitcoin. Because in the end, what’s the prize you win? You don’t know who’s under the mask. You don’t even know who’s under your own mask. Finding a man or woman at a place where half the people are laser-focused on financial sovereignty, and the other half are busy arguing about seed phrase storage, UTXO management, and why your Lightning wallet sucks? But good luck with that. The judge of character usually comes when they find the next shiny object or ditched you standing in the rain at the entrance of a restaurant while dealing with a lightning watchtower or a funny cigarette or whatever. If you’re truly looking for love, maybe stick to going to a normal bar. If you’re here to learn, connect, and be part of something of a grassroots movement, then be real yourself. I've seen some rather nasty examples of people at Bitcoin conferences—of all kinds. And I've also seen some really cool examples of truly awesome people. This led me to believe that Bitcoin conferences simply let you meet… people, just dialed up a bit. Future If you encounter rotten people, they’ll usually be even more rotten than in the fiat world. If you meet really cool people, they’ll be even more awesome than the cool people in the fiat world. Our volatility is our freedom. So, I guess it’s normal. Doesn’t make it any easier, though. Bitcoin sees through bullshit, and so do Bitcoiners (even if it takes 21,000 blocks) Pretty soon, I reckon we’ll see conferences fork into two camps: grass roots, and the “industry” level ones. (human / corporate) I guess I’ll only attend the human part, for sure, but I can’t help but booking myself a single room in a hotel in a nice area in that case, so I don’t have to deal with class of 2022 hippies sharing referral links to their middleman service while asking me for a lighter 3 times in a row. The chances for me of meeting cool bitcoiners in a nearby cocktail bar are a lot higher. In the meanwhile, I’ll look forward and see how the bitcoin conferences will evolve, fork in two “styles”. One corporate and one underground. Maybe there will be one more genre just for the fun of it. I’ll stay away, as I don’t like this current mix of industry gigs and having the insiders and “the rest” of us all mingled together clamoring for tickets, attention and coffee. The game is rigged. Staying at home is the better option (for now). written by AVB If you like : [tip here](https://coinos.io/allesvoorbitcoin/receive) @ f1989a96:bcaaf2c1
2025-04-03 14:30:08Good morning, readers! Georgian officials froze the bank accounts of five nonprofit organizations that provide financial and legal support to detained protesters. This follows rising public unrest as Georgia’s regime pushes new laws restricting free speech and assembly, introducing new fines and penalties, and expanding law enforcement powers. By eroding civil protections, the regime makes it more dangerous and costly for activists, dissenters, and everyday citizens to stand up against an increasingly repressive regime.\ \ Meanwhile, the Indian government introduced a new income tax bill that grants tax authorities sweeping surveillance power over anyone they “suspect” of tax evasion. If suspected, tax authorities are legally allowed to access Indians' email, social media, and bank accounts, raising obvious concerns over state overreach and invasions of individual financial privacy.\ \ In freedom tech news, HRF donated 1 billion satoshis to more than 20 projects worldwide, focusing on supporting human rights defenders and vulnerable communities under authoritarian regimes across Asia, Africa, and Latin America. These gifts advance censorship-resistant communications and transactions, bitcoin education, and privacy tools so that dissidents, nonprofits, and individuals may better protect their human rights and financial freedom. In this letter we also spotlight a new open-source mobile Bitcoin wallet called Cove. While still in beta, the wallet can be used with a hardware device or on its own as a hot wallet, offering a flexible self-custody setup for managing Bitcoin. We end with a podcast in which HRF Chief Strategy Officer Alex Gladstein discusses the state of freedom tech and why Bitcoin stands as the most promising tool for financial liberation. **Now, let’s get right to it!** ### [**SUBSCRIBE HERE**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Georgia | Officials Freeze Accounts of Organizations Supporting Protesters** Georgian officials have [frozen](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) the bank accounts of five nonprofit organizations that provide financial and legal aid to dissenters. This comes in response to an uprising of protests over new controversial laws that restrict free expression and assembly, increase fines and detention periods, and expand law enforcement powers. Georgian officials justify the account freezes as part of an investigation into “sabotage,” yet they have provided no evidence. Amnesty International [warns](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) this financial assault could “kill the entire protest movement.” Bitcoin provides a way to circumvent these struggles. Its uncensorable and permissionless nature has helped [sustain](https://www.journalofdemocracy.org/online-exclusive/how-to-dictator-proof-your-money/) pro-democracy movements across Belarus and Nigeria, proving it is capable of addressing the immense financial restrictions dictators impose. #### **United Arab Emirates | Plans to Launch “Digital Durham” CBDC in 2025** The United Arab Emirates (UAE) will [launch](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) its central bank digital currency (CBDC), the “[Digital Durham](https://cbdctracker.hrf.org/currency/united-arab-emirates),” by the end of 2025. [According](https://www.ledgerinsights.com/uae-to-launch-cbdc-in-q4-2025/) to the central bank, the CBDC will be available through licensed financial institutions and operate via a government-run digital wallet. Every transaction will be recorded on a permissioned blockchain run by the government. The central bank further [admitted](https://u.ae/en/about-the-uae/strategies-initiatives-and-awards/strategies-plans-and-visions/finance-and-economy/central-bank-digital-currency-strategy) the CBDC will replace cash and [assist](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) law enforcement “by leaving a digital trail for transactions involving illicit funds.” Officials [claim](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) this is to combat financial crime, but it also enables real-time surveillance and tracking of individual financial activity. In a country known for strict laws against dissent and extensive surveillance capabilities, it is not hard to see how a CBDC will erode the autonomy and rights of activists, dissenters, and others who oppose an increasingly authoritarian regime. #### **India | Grants Tax Authorities Access to Citizens’ Online Data** Starting in April 2026, the Indian government will [grant](https://economictimes.indiatimes.com/wealth/tax/your-email-and-social-media-account-can-be-accessed-by-income-tax-officer-starting-next-financial-year-in-these-cases/articleshow/118685184.cms) tax authorities legal access to the private online data of any citizen “suspected” of tax evasion. This will include legal access to personal emails, social media, and bank accounts. The new law expands on the Income Tax Act of 1961, which previously limited officials to searching physical premises for financial documents. Now, officials can bypass digital security measures and access private data without consent — all under a legal framework. This dissipation of financial privacy sets an intrusive precedent and opens the door to state-level corruption and surveillance in a country where the Modi regime has already made it clear they are happy to use financial repression to further cement their power. #### **Myanmar | Bitcoin as a Tool Support Earthquake Disaster Relief** Last week, a [7.7 magnitude earthquake](https://www.nytimes.com/2025/03/28/world/asia/earthquake-myanmar-thailand-death-toll.html) struck central Burma, with strong tremors reaching neighboring Thailand. The [official death toll ](https://www.reuters.com/business/environment/survivors-myanmar-quake-left-without-food-water-shelter-aid-groups-say-2025-04-01/)has surpassed 2700. And in Bangkok, a 33-story building under construction [collapsed](https://www.youtube.com/watch?v=ynrhyIh4ozo). Despite an already strenuous situation, Burma’s military junta continues its oppression. They are [blocking](https://www.nytimes.com/2025/03/31/world/asia/myanmar-earthquake-rescue.html) rescue teams from reaching the Sagaing region — the epicenter of the earthquake and the heart of Burma’s pro-democracy movement — and instead channeling aid to regime-controlled cities like Naypyidaw and Mandalay. The junta is also continuing to conduct air strikes on civilians and restricting equipment and fuel for aid groups, leaving a [million](https://data.unhcr.org/en/country/mmr) people in Sagaing to fend for themselves. In these repressive circumstances, Bitcoin can provide a censorship-resistant way to send funds directly to those affected. #### **Angola | Regime Jacks Price of Diesel** The Angolan regime [raised](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) diesel prices by 50% in the process of eliminating fuel subsidies. Diesel prices suddenly increased from 200 to 300 kwanza per liter, driving up transportation costs in a country where over half the population lives on [less](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) than $2 a day and inflation is over 42%. Previous fuel subsidy cuts in 2023 (where the price of diesel rose [80%](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231)) sparked [protests](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) between taxi drivers, nonprofit workers, and law enforcement. This recent price increase now raises fears of renewed crackdowns. The Angolan regime also introduced new civil society laws that Guilherme Neves, chairman of the human rights organization Associacao Maos Livres, [describes](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) as a “license to erase non-governmental organizations that are not government-compliant.” Angolans find themselves in increasingly precarious financial positions as the government erodes the civil safeguards protecting nonprofits and dissenters. #### **Nicaragua | Ortega’s Dismantling of Press Freedom** Since coming to power in 2007, Ortega has [closed or seized](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) 61 media outlets, imprisoned countless journalists, and forced over 280 journalists into exile. His [assault on press freedom](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) has unfolded in two phases: initial raids on local radio stations and TV channels between 2007 and 2017, followed by full-scale censorship in 2018 on independent media outlets like [La Prensa](https://www.laprensani.com/) and [CONFIDENCIAL](https://confidencial.digital/). Ortega then intensified attacks from 2019 to 2021 by closing Nicaragua’s second-oldest newspaper and passing laws to [criminalize](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) free expression. This is a deliberate strategy to eliminate dissent and independent voices. What’s happening in Nicaragua highlights the importance of open and decentralized protocols like nostr, which allow journalists to publish freely without getting censored. While still early, it is becoming essential for sharing information absent the fear of being blocked or silenced by autocratic leaders. ## BITCOIN AND FREEDOM TECH NEWS #### **HRF | Gifts 1 Billion Satoshis to 20+ Open Source Projects Worldwide** HRF gifted 1 billion satoshis in its Q1 2025 round of [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) (BDF) grants, supporting more than 20 open-source projects around the world. These projects advance Bitcoin education, open-source software, mining decentralization, and privacy tools for activists contending with authoritarian regimes across Asia, Latin America, and Africa. Supporting permissionless financial tools and censorship-resistant technologies empowers dissidents, journalists, and civil society to organize, transact, and communicate without state suppression and interference. Learn more about the grantees and their work [here](https://hrf.org/latest/hrf-bitcoin-development-fund-supports-20-projects-worldwide/). #### **Cove | New Open-Source and Permissionless Bitcoin Wallet** [Cove](https://github.com/bitcoinppl/cove) is a new open-source and permissionless mobile Bitcoin wallet that aims to put users in full control of their Bitcoin. Users can connect their own hardware wallet (to manage Bitcoin offline) or use Cove as a hot wallet (to manage Bitcoin online). It also allows users to create multiple wallets from the app itself. In the future, Cove plans to add Unspent Transaction Output (UTXO) selection and coin control, giving users more independence over their transactions and the tools to better protect their financial privacy. While still in beta and only suitable for test funds, this wallet holds promise as a privacy tool to equip dissidents with self-custodied Bitcoin. You can try it [here](https://github.com/bitcoinppl/cove). #### **Second | New Ark Implementation Launches on Bitcoin Signet** [Second](https://second.tech/), a company building on Ark, a protocol designed to help scale Bitcoin’s transaction throughput, [launched](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com) “Bark.” Bark is a test implementation of the Ark protocol deployed on Bitcoin’s [Signet](https://en.bitcoin.it/wiki/Signet) network (where developers test software). More broadly, the Ark protocol helps make Bitcoin transactions more private, faster, and cheaper, supporting the network in handling more transactions and users with the tradeoff of being less trusted than the mainchain, as funds stored in a noncustodial way on Ark can expire if not used. While it is still in early development, the test release of Bark marks a step toward deployment on the main Bitcoin network. Scaling solutions like Ark could be important for activists and individuals. They might ensure Bitcoin remains accessible to all, even as block space demand increases and network fees rise. Learn about it [here](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com). #### **Braiins | Open Sources Bitcoin Control Board** [Braiins](https://braiins.com/), a company building tools for Bitcoin mining, [open-sourced](https://x.com/BraiinsMining/status/1904601547855573458) its [BCB100](https://github.com/braiins/BCB100) Bitcoin Control Board, giving miners using their products greater insight and control over their Bitcoin mining hardware and firmware. Sharing the design files and firmware openly helps strengthen Bitcoin’s decentralization, making it more resilient against corporate or state interference. Specifically, open-sourcing mining hardware ensures individual miners can operate independently, reducing censorship risks across the entire network. In turn, this preserves financial freedom by keeping Bitcoin accessible and usable by dissidents, nonprofits, and individuals who need it most. #### **African Bitcoiners | Publish Bitcoin Starter Guide** [African Bitcoiners](https://x.com/afribitcoiners) just published “[Bitcoin: Africa’s Guide to Freedom Money](https://x.com/afribitcoiners/status/1904516726273851513),” a Bitcoin guide providing clear, practical insights into how Bitcoin can help people across the continent escape inflation, corrupt regimes, and failing financial systems. It covers essential topics to get started — from choosing a wallet to properly securing Bitcoin. In Africa, where some of the world’s longest-standing dictators restrict even basic financial activity, this guide is a powerful resource for human rights defenders, nonprofits, and everyday citizens. Read it[ here](https://bitcoiners.africa/bitcoin-africas-guide-to-freedom-money/). #### **OpenSats | 10th Wave of Nostr Grants** [OpenSats](https://opensats.org/), a nonprofit that supports open-source software development, [announced](https://opensats.org/blog/10th-wave-of-nostr-grants) its tenth wave of grants for projects in the nostr ecosystem. Nostr is a decentralized protocol that enables digital identity and communications outside the reach of authoritarian states. The grant round provides support to nostr Epoxy, which enhances access to nostr by circumventing censorship through a network of paid proxies. This ensures activists and dissidents can continue to communicate even in restrictive environments. Additionally, Zapstore received a grant for providing a permissionless app store built on nostr that enables developers to distribute software without corporate gatekeepers. This provides an open-source alternative to centralized app stores that often comply with government censorship and restrict dissidents’ access to freedom tools. ## RECOMMENDED CONTENT #### **Freedom Tech with Alex Gladstein** In this [episode](https://x.com/blockspacepod/status/1896229100702089589?s=46&t=yEPKerGEzeCp5j_mIaNJ8A) of The Gwart Show, Alex Gladstein, chief strategy officer at HRF, breaks down how and why Bitcoin serves as “money dictators can’t stop.” Drawing on more than 17 years of human rights work, he shares real-world examples of activists and citizens using Bitcoin to escape financial repression in authoritarian countries. Gladstein also explores privacy tools, cross-border payments, and why Bitcoin offers promising hope for financial freedom. Watch the full conversation [here](https://www.youtube.com/watch?v=5Ng961QZwI0). #### **The State of Personal Online Security and Confidentiality with Meredith Whittaker** In this [keynote](https://www.youtube.com/watch?v=AyH7zoP-JOg) for SXSW 2025, Signal CEO Meredith Whittaker shares her growing concerns around AI, personal data collection, and the erosion of privacy in today’s increasingly digital world. She emphasizes the need for more secure, uncensorable, and privacy-protecting technologies that shield users from surveillance and exploitation, especially in the context of authoritarian regimes. Watch the [full discussion](https://www.youtube.com/watch?v=AyH7zoP-JOg) for a pragmatic view into the future of digital privacy and security. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/)
@ f1989a96:bcaaf2c1
2025-04-03 14:30:08Good morning, readers! Georgian officials froze the bank accounts of five nonprofit organizations that provide financial and legal support to detained protesters. This follows rising public unrest as Georgia’s regime pushes new laws restricting free speech and assembly, introducing new fines and penalties, and expanding law enforcement powers. By eroding civil protections, the regime makes it more dangerous and costly for activists, dissenters, and everyday citizens to stand up against an increasingly repressive regime.\ \ Meanwhile, the Indian government introduced a new income tax bill that grants tax authorities sweeping surveillance power over anyone they “suspect” of tax evasion. If suspected, tax authorities are legally allowed to access Indians' email, social media, and bank accounts, raising obvious concerns over state overreach and invasions of individual financial privacy.\ \ In freedom tech news, HRF donated 1 billion satoshis to more than 20 projects worldwide, focusing on supporting human rights defenders and vulnerable communities under authoritarian regimes across Asia, Africa, and Latin America. These gifts advance censorship-resistant communications and transactions, bitcoin education, and privacy tools so that dissidents, nonprofits, and individuals may better protect their human rights and financial freedom. In this letter we also spotlight a new open-source mobile Bitcoin wallet called Cove. While still in beta, the wallet can be used with a hardware device or on its own as a hot wallet, offering a flexible self-custody setup for managing Bitcoin. We end with a podcast in which HRF Chief Strategy Officer Alex Gladstein discusses the state of freedom tech and why Bitcoin stands as the most promising tool for financial liberation. **Now, let’s get right to it!** ### [**SUBSCRIBE HERE**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Georgia | Officials Freeze Accounts of Organizations Supporting Protesters** Georgian officials have [frozen](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) the bank accounts of five nonprofit organizations that provide financial and legal aid to dissenters. This comes in response to an uprising of protests over new controversial laws that restrict free expression and assembly, increase fines and detention periods, and expand law enforcement powers. Georgian officials justify the account freezes as part of an investigation into “sabotage,” yet they have provided no evidence. Amnesty International [warns](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) this financial assault could “kill the entire protest movement.” Bitcoin provides a way to circumvent these struggles. Its uncensorable and permissionless nature has helped [sustain](https://www.journalofdemocracy.org/online-exclusive/how-to-dictator-proof-your-money/) pro-democracy movements across Belarus and Nigeria, proving it is capable of addressing the immense financial restrictions dictators impose. #### **United Arab Emirates | Plans to Launch “Digital Durham” CBDC in 2025** The United Arab Emirates (UAE) will [launch](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) its central bank digital currency (CBDC), the “[Digital Durham](https://cbdctracker.hrf.org/currency/united-arab-emirates),” by the end of 2025. [According](https://www.ledgerinsights.com/uae-to-launch-cbdc-in-q4-2025/) to the central bank, the CBDC will be available through licensed financial institutions and operate via a government-run digital wallet. Every transaction will be recorded on a permissioned blockchain run by the government. The central bank further [admitted](https://u.ae/en/about-the-uae/strategies-initiatives-and-awards/strategies-plans-and-visions/finance-and-economy/central-bank-digital-currency-strategy) the CBDC will replace cash and [assist](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) law enforcement “by leaving a digital trail for transactions involving illicit funds.” Officials [claim](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) this is to combat financial crime, but it also enables real-time surveillance and tracking of individual financial activity. In a country known for strict laws against dissent and extensive surveillance capabilities, it is not hard to see how a CBDC will erode the autonomy and rights of activists, dissenters, and others who oppose an increasingly authoritarian regime. #### **India | Grants Tax Authorities Access to Citizens’ Online Data** Starting in April 2026, the Indian government will [grant](https://economictimes.indiatimes.com/wealth/tax/your-email-and-social-media-account-can-be-accessed-by-income-tax-officer-starting-next-financial-year-in-these-cases/articleshow/118685184.cms) tax authorities legal access to the private online data of any citizen “suspected” of tax evasion. This will include legal access to personal emails, social media, and bank accounts. The new law expands on the Income Tax Act of 1961, which previously limited officials to searching physical premises for financial documents. Now, officials can bypass digital security measures and access private data without consent — all under a legal framework. This dissipation of financial privacy sets an intrusive precedent and opens the door to state-level corruption and surveillance in a country where the Modi regime has already made it clear they are happy to use financial repression to further cement their power. #### **Myanmar | Bitcoin as a Tool Support Earthquake Disaster Relief** Last week, a [7.7 magnitude earthquake](https://www.nytimes.com/2025/03/28/world/asia/earthquake-myanmar-thailand-death-toll.html) struck central Burma, with strong tremors reaching neighboring Thailand. The [official death toll ](https://www.reuters.com/business/environment/survivors-myanmar-quake-left-without-food-water-shelter-aid-groups-say-2025-04-01/)has surpassed 2700. And in Bangkok, a 33-story building under construction [collapsed](https://www.youtube.com/watch?v=ynrhyIh4ozo). Despite an already strenuous situation, Burma’s military junta continues its oppression. They are [blocking](https://www.nytimes.com/2025/03/31/world/asia/myanmar-earthquake-rescue.html) rescue teams from reaching the Sagaing region — the epicenter of the earthquake and the heart of Burma’s pro-democracy movement — and instead channeling aid to regime-controlled cities like Naypyidaw and Mandalay. The junta is also continuing to conduct air strikes on civilians and restricting equipment and fuel for aid groups, leaving a [million](https://data.unhcr.org/en/country/mmr) people in Sagaing to fend for themselves. In these repressive circumstances, Bitcoin can provide a censorship-resistant way to send funds directly to those affected. #### **Angola | Regime Jacks Price of Diesel** The Angolan regime [raised](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) diesel prices by 50% in the process of eliminating fuel subsidies. Diesel prices suddenly increased from 200 to 300 kwanza per liter, driving up transportation costs in a country where over half the population lives on [less](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) than $2 a day and inflation is over 42%. Previous fuel subsidy cuts in 2023 (where the price of diesel rose [80%](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231)) sparked [protests](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) between taxi drivers, nonprofit workers, and law enforcement. This recent price increase now raises fears of renewed crackdowns. The Angolan regime also introduced new civil society laws that Guilherme Neves, chairman of the human rights organization Associacao Maos Livres, [describes](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) as a “license to erase non-governmental organizations that are not government-compliant.” Angolans find themselves in increasingly precarious financial positions as the government erodes the civil safeguards protecting nonprofits and dissenters. #### **Nicaragua | Ortega’s Dismantling of Press Freedom** Since coming to power in 2007, Ortega has [closed or seized](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) 61 media outlets, imprisoned countless journalists, and forced over 280 journalists into exile. His [assault on press freedom](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) has unfolded in two phases: initial raids on local radio stations and TV channels between 2007 and 2017, followed by full-scale censorship in 2018 on independent media outlets like [La Prensa](https://www.laprensani.com/) and [CONFIDENCIAL](https://confidencial.digital/). Ortega then intensified attacks from 2019 to 2021 by closing Nicaragua’s second-oldest newspaper and passing laws to [criminalize](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) free expression. This is a deliberate strategy to eliminate dissent and independent voices. What’s happening in Nicaragua highlights the importance of open and decentralized protocols like nostr, which allow journalists to publish freely without getting censored. While still early, it is becoming essential for sharing information absent the fear of being blocked or silenced by autocratic leaders. ## BITCOIN AND FREEDOM TECH NEWS #### **HRF | Gifts 1 Billion Satoshis to 20+ Open Source Projects Worldwide** HRF gifted 1 billion satoshis in its Q1 2025 round of [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) (BDF) grants, supporting more than 20 open-source projects around the world. These projects advance Bitcoin education, open-source software, mining decentralization, and privacy tools for activists contending with authoritarian regimes across Asia, Latin America, and Africa. Supporting permissionless financial tools and censorship-resistant technologies empowers dissidents, journalists, and civil society to organize, transact, and communicate without state suppression and interference. Learn more about the grantees and their work [here](https://hrf.org/latest/hrf-bitcoin-development-fund-supports-20-projects-worldwide/). #### **Cove | New Open-Source and Permissionless Bitcoin Wallet** [Cove](https://github.com/bitcoinppl/cove) is a new open-source and permissionless mobile Bitcoin wallet that aims to put users in full control of their Bitcoin. Users can connect their own hardware wallet (to manage Bitcoin offline) or use Cove as a hot wallet (to manage Bitcoin online). It also allows users to create multiple wallets from the app itself. In the future, Cove plans to add Unspent Transaction Output (UTXO) selection and coin control, giving users more independence over their transactions and the tools to better protect their financial privacy. While still in beta and only suitable for test funds, this wallet holds promise as a privacy tool to equip dissidents with self-custodied Bitcoin. You can try it [here](https://github.com/bitcoinppl/cove). #### **Second | New Ark Implementation Launches on Bitcoin Signet** [Second](https://second.tech/), a company building on Ark, a protocol designed to help scale Bitcoin’s transaction throughput, [launched](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com) “Bark.” Bark is a test implementation of the Ark protocol deployed on Bitcoin’s [Signet](https://en.bitcoin.it/wiki/Signet) network (where developers test software). More broadly, the Ark protocol helps make Bitcoin transactions more private, faster, and cheaper, supporting the network in handling more transactions and users with the tradeoff of being less trusted than the mainchain, as funds stored in a noncustodial way on Ark can expire if not used. While it is still in early development, the test release of Bark marks a step toward deployment on the main Bitcoin network. Scaling solutions like Ark could be important for activists and individuals. They might ensure Bitcoin remains accessible to all, even as block space demand increases and network fees rise. Learn about it [here](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com). #### **Braiins | Open Sources Bitcoin Control Board** [Braiins](https://braiins.com/), a company building tools for Bitcoin mining, [open-sourced](https://x.com/BraiinsMining/status/1904601547855573458) its [BCB100](https://github.com/braiins/BCB100) Bitcoin Control Board, giving miners using their products greater insight and control over their Bitcoin mining hardware and firmware. Sharing the design files and firmware openly helps strengthen Bitcoin’s decentralization, making it more resilient against corporate or state interference. Specifically, open-sourcing mining hardware ensures individual miners can operate independently, reducing censorship risks across the entire network. In turn, this preserves financial freedom by keeping Bitcoin accessible and usable by dissidents, nonprofits, and individuals who need it most. #### **African Bitcoiners | Publish Bitcoin Starter Guide** [African Bitcoiners](https://x.com/afribitcoiners) just published “[Bitcoin: Africa’s Guide to Freedom Money](https://x.com/afribitcoiners/status/1904516726273851513),” a Bitcoin guide providing clear, practical insights into how Bitcoin can help people across the continent escape inflation, corrupt regimes, and failing financial systems. It covers essential topics to get started — from choosing a wallet to properly securing Bitcoin. In Africa, where some of the world’s longest-standing dictators restrict even basic financial activity, this guide is a powerful resource for human rights defenders, nonprofits, and everyday citizens. Read it[ here](https://bitcoiners.africa/bitcoin-africas-guide-to-freedom-money/). #### **OpenSats | 10th Wave of Nostr Grants** [OpenSats](https://opensats.org/), a nonprofit that supports open-source software development, [announced](https://opensats.org/blog/10th-wave-of-nostr-grants) its tenth wave of grants for projects in the nostr ecosystem. Nostr is a decentralized protocol that enables digital identity and communications outside the reach of authoritarian states. The grant round provides support to nostr Epoxy, which enhances access to nostr by circumventing censorship through a network of paid proxies. This ensures activists and dissidents can continue to communicate even in restrictive environments. Additionally, Zapstore received a grant for providing a permissionless app store built on nostr that enables developers to distribute software without corporate gatekeepers. This provides an open-source alternative to centralized app stores that often comply with government censorship and restrict dissidents’ access to freedom tools. ## RECOMMENDED CONTENT #### **Freedom Tech with Alex Gladstein** In this [episode](https://x.com/blockspacepod/status/1896229100702089589?s=46&t=yEPKerGEzeCp5j_mIaNJ8A) of The Gwart Show, Alex Gladstein, chief strategy officer at HRF, breaks down how and why Bitcoin serves as “money dictators can’t stop.” Drawing on more than 17 years of human rights work, he shares real-world examples of activists and citizens using Bitcoin to escape financial repression in authoritarian countries. Gladstein also explores privacy tools, cross-border payments, and why Bitcoin offers promising hope for financial freedom. Watch the full conversation [here](https://www.youtube.com/watch?v=5Ng961QZwI0). #### **The State of Personal Online Security and Confidentiality with Meredith Whittaker** In this [keynote](https://www.youtube.com/watch?v=AyH7zoP-JOg) for SXSW 2025, Signal CEO Meredith Whittaker shares her growing concerns around AI, personal data collection, and the erosion of privacy in today’s increasingly digital world. She emphasizes the need for more secure, uncensorable, and privacy-protecting technologies that shield users from surveillance and exploitation, especially in the context of authoritarian regimes. Watch the [full discussion](https://www.youtube.com/watch?v=AyH7zoP-JOg) for a pragmatic view into the future of digital privacy and security. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/) @ 1aa9ff07:3cb793b5
2025-04-03 14:06:38In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement. **Understanding Nostr: A Decentralized Social Network Protocol** In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement.
@ 1aa9ff07:3cb793b5
2025-04-03 14:06:38In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement. **Understanding Nostr: A Decentralized Social Network Protocol** In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement. @ edeb837b:ac664163
2025-04-03 10:35:59When it comes to social trading, there are plenty of platforms that claim to offer innovative ways to connect with other traders, share strategies, and improve your market performance. But let's be real: most so-called "social trading" apps are either glorified brokerage platforms with limited community features or outdated, clunky systems that don’t offer real-time value. There’s really only *one* social trading app you need to consider—**NVSTly**. Here’s why. ## Why NVSTly Stands Above the Rest NVSTly isn’t just another trading app with a few social features slapped on. It’s **the ultimate [social trading platform](https://nvstly.com)**, purpose-built to empower traders by combining **real-time trade tracking, seamless social sharing, deep market insights, and a powerful trader community.** Unlike other platforms, NVSTly isn’t just about copying trades or following vague signals—it’s about **true transparency, collaboration, and learning** from top traders in an interactive environment. ## What is NVSTly? **NVSTly** is a **completely free** social trading platform that lets traders track, share, and analyze their trades in **real time**. Whether you're trading **stocks, options, or crypto**, NVSTly provides a **seamless multi-platform experience**—available via **web, iOS, Android, and even Discord.** It’s not just a social network—it’s a **trader’s command center** where every trade you make is part of a bigger, smarter ecosystem designed to help you grow. ## Key Features That Make NVSTly #1 ### 1. Real-Time Trade Sharing & Tracking NVSTly integrates with brokers like **Webull** (with more brokerages coming soon) to automatically track your trades and display them in **real-time**. No manual entry—just **instant trade updates** for you and your followers. ### 2. Unique POV Trade Charting See trades like never before. NVSTly’s proprietary **POV Chart** marks every trade action directly on the candlestick chart, giving you (and your followers) an **unparalleled view of trading strategies in action**. ### 3. Deep Trade Analytics & Trader Dashboards Get powerful insights into your performance, including: - **Win rate** - **Total gain/loss** - **Average return per trade** - **Long vs. short ratio** - **(Coming soon) Drawdown tracking** to measure risk exposure ### 4. Global Trades Feed & Leaderboard Want to see what the best traders are doing *right now*? The **[Global Trades Feed](https://nvstly.com/trades)** lets you watch live trades, while the **[Leaderboard](https://nvstly.com/trades)** ranks top traders based on performance metrics, making it easy to find successful strategies. ### 5. Fully Integrated with Discord & Telegram No other platform makes social trading as seamless as NVSTly. The **[NVSTly Discord bot](https://nvstly.com/go/bot)** allows users to: - **Check a trader’s latest stats** - **View real-time trade recaps** - **Fetch charts and ticker data** - **Receive automated trade notifications** Telegram users won’t be left out either—NVSTly is working on bringing the same functionality to **Telegram** for even broader access. ### 6. Automated Social Media Sharing Set your trades to **automatically share** to **Twitter/X, Discord, and soon, Telegram**. Whether you’re growing your personal brand or running a trading community, NVSTly makes sure your trades get noticed. ### 7. Future AI & Machine Learning Enhancements NVSTly is building **AI-powered trade insights and strategy generation**, allowing traders to: - **Get automated trading tips** tailored to their strategies - **Use customizable AI models** to refine their trading approach - **Interact with a smart AI trading assistant** via the app and Discord bot ## Why NVSTly is the Only Social Trading App You Need While others might pretend to offer social trading, **NVSTly actually delivers**. It’s not a gimmick or a half-baked feature—it’s a complete **trading ecosystem built for real traders** who want **real-time data, powerful analytics, and a truly social experience.** With NVSTly, you're not just following traders—you’re **engaging with them, learning from them, and improving your own strategies** in the most **transparent and interactive** way possible. So don’t waste time on inferior platforms. **NVSTly is the only social trading app that matters.** ## Ready to Take Your Trading to the Next Level? Join **50,000+ traders** who are already using NVSTly to **track, share, and dominate the markets.** 📲 **Download NVSTly today on [Web](https://nvstly.com), [iOS](https://nvstly.com/go/ios), or [Android](https://nvstly.com/go/android)!** 🚀 **[Join our Discord community](https://nvstly.com/go/discord)** and bring the power of NVSTly straight into your server!
@ edeb837b:ac664163
2025-04-03 10:35:59When it comes to social trading, there are plenty of platforms that claim to offer innovative ways to connect with other traders, share strategies, and improve your market performance. But let's be real: most so-called "social trading" apps are either glorified brokerage platforms with limited community features or outdated, clunky systems that don’t offer real-time value. There’s really only *one* social trading app you need to consider—**NVSTly**. Here’s why. ## Why NVSTly Stands Above the Rest NVSTly isn’t just another trading app with a few social features slapped on. It’s **the ultimate [social trading platform](https://nvstly.com)**, purpose-built to empower traders by combining **real-time trade tracking, seamless social sharing, deep market insights, and a powerful trader community.** Unlike other platforms, NVSTly isn’t just about copying trades or following vague signals—it’s about **true transparency, collaboration, and learning** from top traders in an interactive environment. ## What is NVSTly? **NVSTly** is a **completely free** social trading platform that lets traders track, share, and analyze their trades in **real time**. Whether you're trading **stocks, options, or crypto**, NVSTly provides a **seamless multi-platform experience**—available via **web, iOS, Android, and even Discord.** It’s not just a social network—it’s a **trader’s command center** where every trade you make is part of a bigger, smarter ecosystem designed to help you grow. ## Key Features That Make NVSTly #1 ### 1. Real-Time Trade Sharing & Tracking NVSTly integrates with brokers like **Webull** (with more brokerages coming soon) to automatically track your trades and display them in **real-time**. No manual entry—just **instant trade updates** for you and your followers. ### 2. Unique POV Trade Charting See trades like never before. NVSTly’s proprietary **POV Chart** marks every trade action directly on the candlestick chart, giving you (and your followers) an **unparalleled view of trading strategies in action**. ### 3. Deep Trade Analytics & Trader Dashboards Get powerful insights into your performance, including: - **Win rate** - **Total gain/loss** - **Average return per trade** - **Long vs. short ratio** - **(Coming soon) Drawdown tracking** to measure risk exposure ### 4. Global Trades Feed & Leaderboard Want to see what the best traders are doing *right now*? The **[Global Trades Feed](https://nvstly.com/trades)** lets you watch live trades, while the **[Leaderboard](https://nvstly.com/trades)** ranks top traders based on performance metrics, making it easy to find successful strategies. ### 5. Fully Integrated with Discord & Telegram No other platform makes social trading as seamless as NVSTly. The **[NVSTly Discord bot](https://nvstly.com/go/bot)** allows users to: - **Check a trader’s latest stats** - **View real-time trade recaps** - **Fetch charts and ticker data** - **Receive automated trade notifications** Telegram users won’t be left out either—NVSTly is working on bringing the same functionality to **Telegram** for even broader access. ### 6. Automated Social Media Sharing Set your trades to **automatically share** to **Twitter/X, Discord, and soon, Telegram**. Whether you’re growing your personal brand or running a trading community, NVSTly makes sure your trades get noticed. ### 7. Future AI & Machine Learning Enhancements NVSTly is building **AI-powered trade insights and strategy generation**, allowing traders to: - **Get automated trading tips** tailored to their strategies - **Use customizable AI models** to refine their trading approach - **Interact with a smart AI trading assistant** via the app and Discord bot ## Why NVSTly is the Only Social Trading App You Need While others might pretend to offer social trading, **NVSTly actually delivers**. It’s not a gimmick or a half-baked feature—it’s a complete **trading ecosystem built for real traders** who want **real-time data, powerful analytics, and a truly social experience.** With NVSTly, you're not just following traders—you’re **engaging with them, learning from them, and improving your own strategies** in the most **transparent and interactive** way possible. So don’t waste time on inferior platforms. **NVSTly is the only social trading app that matters.** ## Ready to Take Your Trading to the Next Level? Join **50,000+ traders** who are already using NVSTly to **track, share, and dominate the markets.** 📲 **Download NVSTly today on [Web](https://nvstly.com), [iOS](https://nvstly.com/go/ios), or [Android](https://nvstly.com/go/android)!** 🚀 **[Join our Discord community](https://nvstly.com/go/discord)** and bring the power of NVSTly straight into your server! @ e4950c93:1b99eccd
2025-04-03 09:55:59### Équipe Cœur L'équipe Cœur porte le projet et valide les contenus. - [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) Pour démarrer, je gère le projet en solo. Contactez-moi si vous souhaitez rejoindre l'aventure ! ### Enrichisseu-r-se-s de contenus Les contribut-eur-rice-s rendent ce site vivant et intéressant.
@ e4950c93:1b99eccd
2025-04-03 09:55:59### Équipe Cœur L'équipe Cœur porte le projet et valide les contenus. - [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) Pour démarrer, je gère le projet en solo. Contactez-moi si vous souhaitez rejoindre l'aventure ! ### Enrichisseu-r-se-s de contenus Les contribut-eur-rice-s rendent ce site vivant et intéressant. @ 77c2969e:a33cfa50
2025-04-03 07:54:55最近又开始折腾 Technitium DNS Server,发现[之前记录的过程]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)不太完善,于是更新一下。 #### 安装acme.sh ``` curl https://get.acme.sh | sh -s email=youreMailAddress ``` #### 导入环境变量 ``` export CF_Token="填API token" export CF_Zone_ID="填区域ID" export CF_Account_ID="填账户ID" ``` - Cloudflare 的 API Token 是在 Cloudflare 网页右上角的👤头像--配置文件--API 令牌处创建 - 在 Cloudflare 主页点击你需要使用的域名,下滑到右下角可以看到区域 ID 和账户 ID ### 申请证书 ``` acme.sh --issue --dns dns_cf -d dns.235421.xyz ``` - `-d` 后面是你想使用的域名 #### 安装证书 ``` acme.sh --install-cert -d dns.235421.xyz \ --key-file /root/certs/key.pem \ --fullchain-file /root/certs/cert.pem \ --reloadcmd "cd /root/certs && openssl pkcs12 -export -out 'dns.pfx' -inkey 'key.pem' -in 'cert.pem' -password pass:1021" ``` - `reloadcmd`是在申请证书之后执行的代码,以后自动更新时也会自动执行这个代码,所以第一次配置好就基本上不用管了。 - `reloadcmd` 中的代码是将 `pem` 格式的证书和密钥转换成一个 `pfx` 格式的证书文件,`-out` 后面是输出的 `pfx` 证书文件名, `-inkey` 和 `-in` 分别是前一步 `acme.sh` 申请的密钥和证书文件。这里必须添加密码,也就是 `1021` 这个,如果不设密码执行命令的话,它会让你交互式输入,但是在自动脚本中就不行。我在前面加了先 `cd` 到证书目录,避免出现问题。 #### 安装 Technitium DNS Server 1. 在[Technitium DNS Server 官网]( https://technitium.com/dns/) 获取安装脚本,也有提供 Docker 镜像以及 Windows 版本。  2. 安装后在 `公网IP:5380` 进入管理界面,首次进入需设置管理员密码,管理员账户默认是 `admin`。 3. 在 `Settings` – `optional protocols` 处开启 DNS over HTTPS ,`TLS Certificate File Path` 处填入转换好的 `pfx` 证书路径,`TLS Certificate Password` 处填你设定的密码,就是我的 `1021` 。 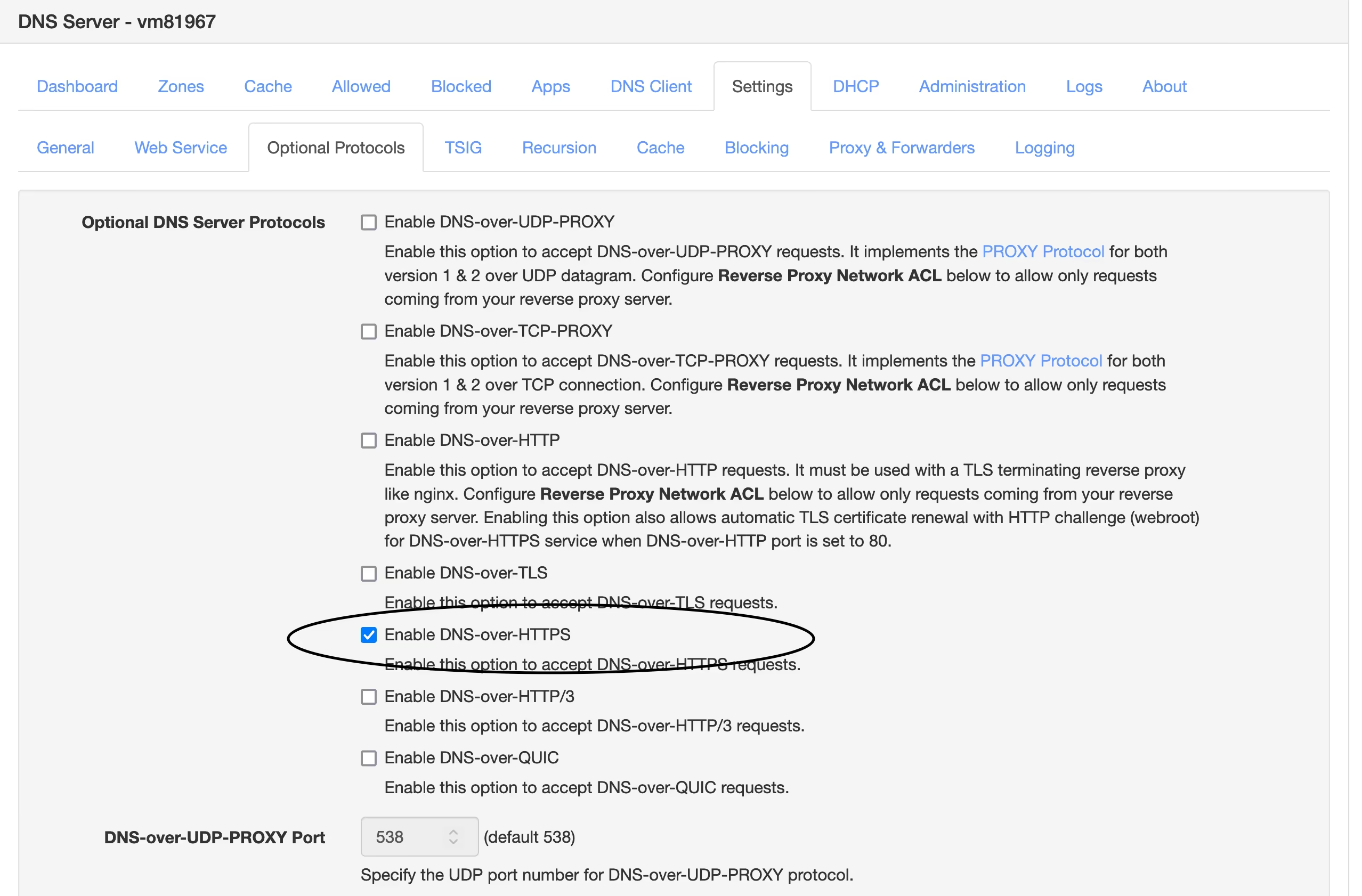 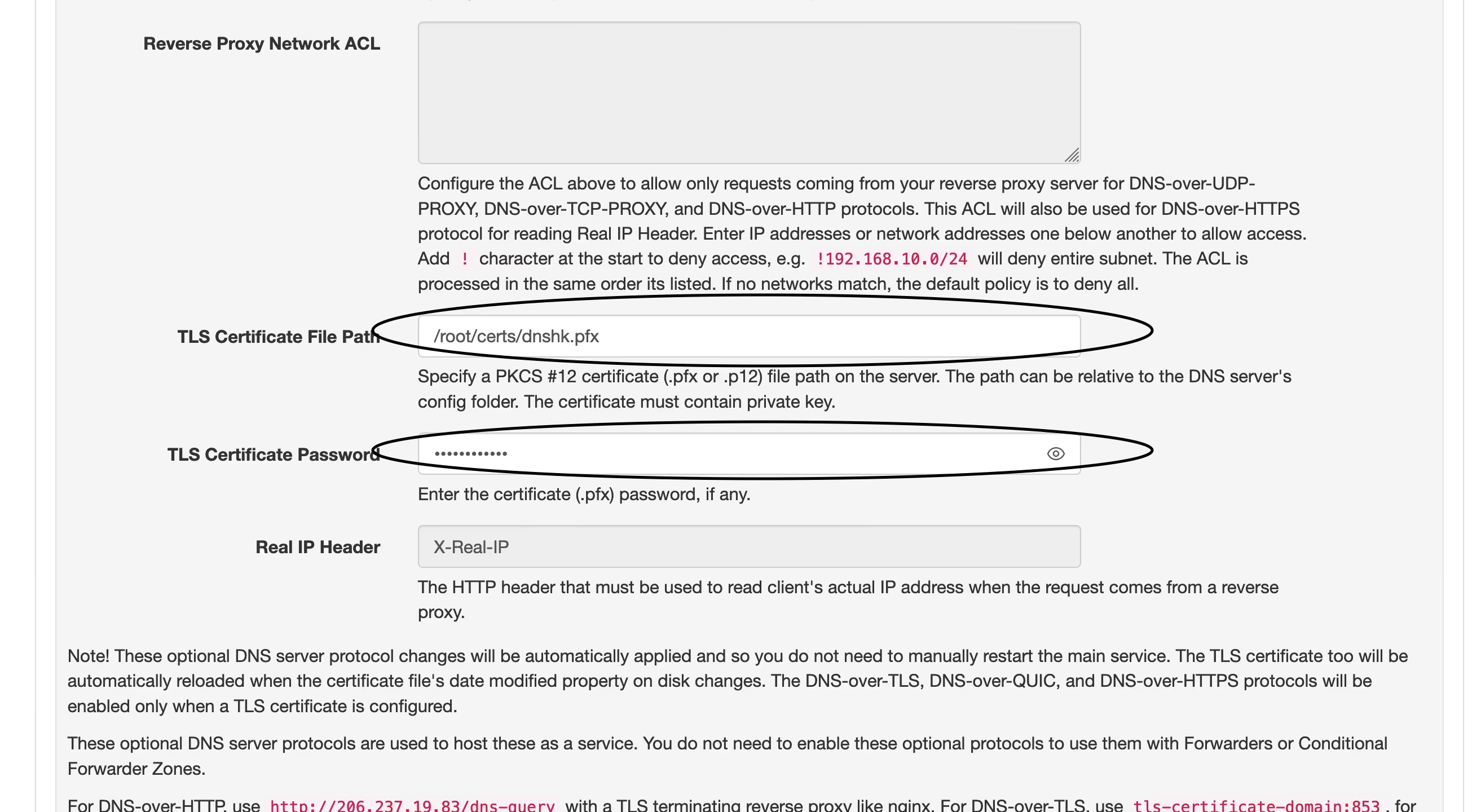 4. 现在打开你的域名,看到如图这样就说明设定成功了,然后在需要设置 DoH 的地方填入 ` https://yourdomain.com/dns-query`即可。 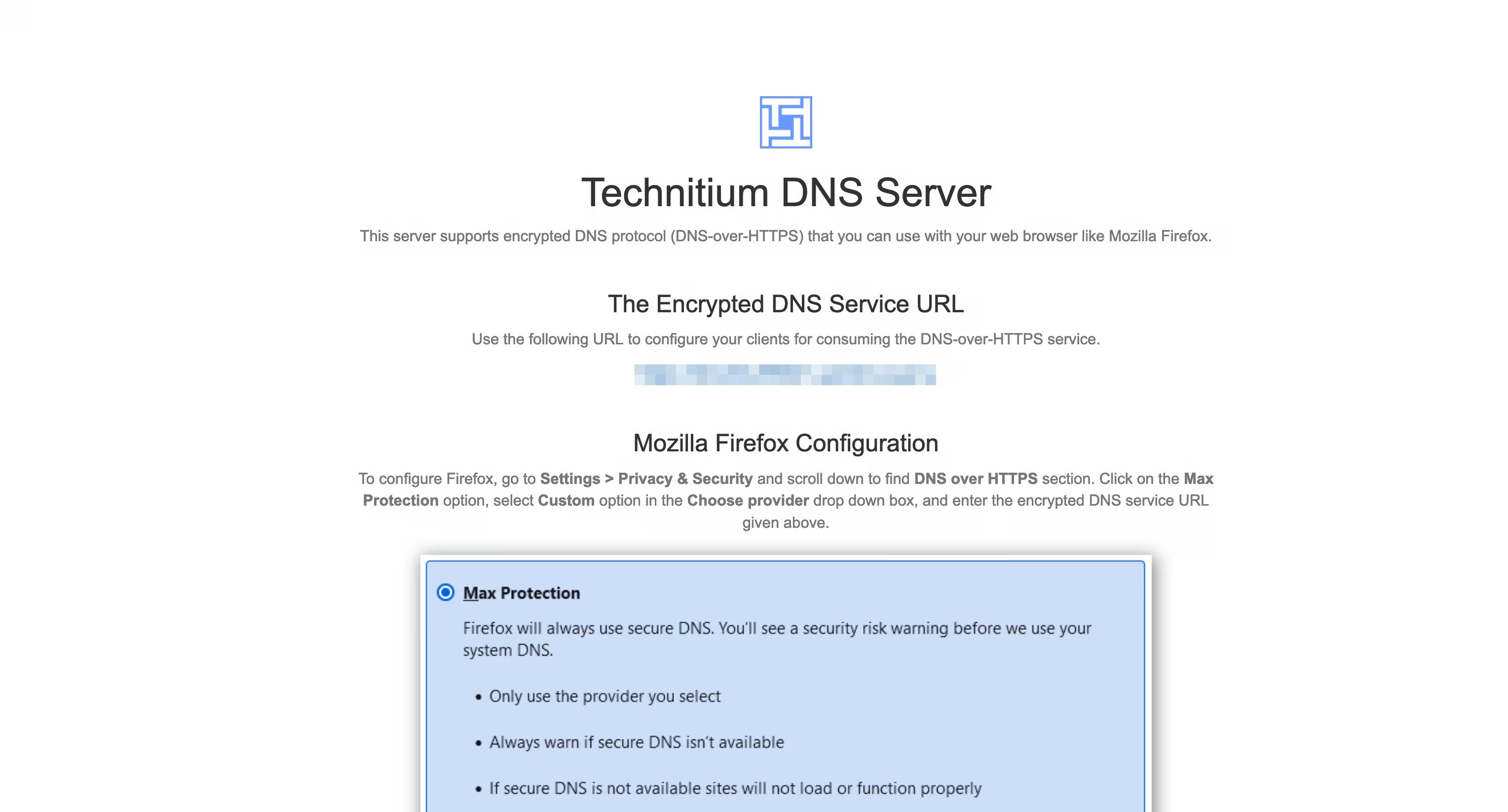 ---- 我在[之前的文章]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)中使用的是 `DNS over HTTP` 并用 Nginx 反代来实现 `DNS over HTTPS` 的,现在直接用 DoH ,省去了配置 Nginx 的部分,只是多了一步证书格式转换,总体上更简单了。 ---- #### 我的设置 - 在`Settings` – `Recursion` 处打开 `Allow Recursion` 以允许递归解析。 - 在`Settings` – `Cache` 处将 `Cache Maximum Entries` 调大些,默认 10000 有点少了。 - 在`Settings` – `General` 处开启 `EDNS Client Subnet (ECS)` 。 - 在`Settings` – `Logging` 处开启 `Use Local Time`。 - 在`Apps` – `App Store` 中安装 `Query Logs (Sqlite)` 以便在 `Logs` – `Query Logs` 处查看 DNS 查询日志。 ##### 以下设置可选 - 在`Settings` – `General` 处开启 `Prefer IPv6` - 在`Settings` – `Web Service` 处为后台管理页面开启 HTTPS,可使用与 DoH 相同的域名和证书,仅端口不同,这个默认 HTTPS 端口是 `53443`。 - 在`Settings` – `Blocking` 处开启拦截功能(默认开启),下面 `Allow / Block List URLs` 可以配置规则,与 AdGuard Home 规则通用,白名单规则须在链接前加上英文叹号 `!`。也可以是本地规则,填路径即可。 - 在`Settings` – `Proxy & Forwarders` 处可以设置上游DNS `Forwarders` 。
@ 77c2969e:a33cfa50
2025-04-03 07:54:55最近又开始折腾 Technitium DNS Server,发现[之前记录的过程]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)不太完善,于是更新一下。 #### 安装acme.sh ``` curl https://get.acme.sh | sh -s email=youreMailAddress ``` #### 导入环境变量 ``` export CF_Token="填API token" export CF_Zone_ID="填区域ID" export CF_Account_ID="填账户ID" ``` - Cloudflare 的 API Token 是在 Cloudflare 网页右上角的👤头像--配置文件--API 令牌处创建 - 在 Cloudflare 主页点击你需要使用的域名,下滑到右下角可以看到区域 ID 和账户 ID ### 申请证书 ``` acme.sh --issue --dns dns_cf -d dns.235421.xyz ``` - `-d` 后面是你想使用的域名 #### 安装证书 ``` acme.sh --install-cert -d dns.235421.xyz \ --key-file /root/certs/key.pem \ --fullchain-file /root/certs/cert.pem \ --reloadcmd "cd /root/certs && openssl pkcs12 -export -out 'dns.pfx' -inkey 'key.pem' -in 'cert.pem' -password pass:1021" ``` - `reloadcmd`是在申请证书之后执行的代码,以后自动更新时也会自动执行这个代码,所以第一次配置好就基本上不用管了。 - `reloadcmd` 中的代码是将 `pem` 格式的证书和密钥转换成一个 `pfx` 格式的证书文件,`-out` 后面是输出的 `pfx` 证书文件名, `-inkey` 和 `-in` 分别是前一步 `acme.sh` 申请的密钥和证书文件。这里必须添加密码,也就是 `1021` 这个,如果不设密码执行命令的话,它会让你交互式输入,但是在自动脚本中就不行。我在前面加了先 `cd` 到证书目录,避免出现问题。 #### 安装 Technitium DNS Server 1. 在[Technitium DNS Server 官网]( https://technitium.com/dns/) 获取安装脚本,也有提供 Docker 镜像以及 Windows 版本。  2. 安装后在 `公网IP:5380` 进入管理界面,首次进入需设置管理员密码,管理员账户默认是 `admin`。 3. 在 `Settings` – `optional protocols` 处开启 DNS over HTTPS ,`TLS Certificate File Path` 处填入转换好的 `pfx` 证书路径,`TLS Certificate Password` 处填你设定的密码,就是我的 `1021` 。 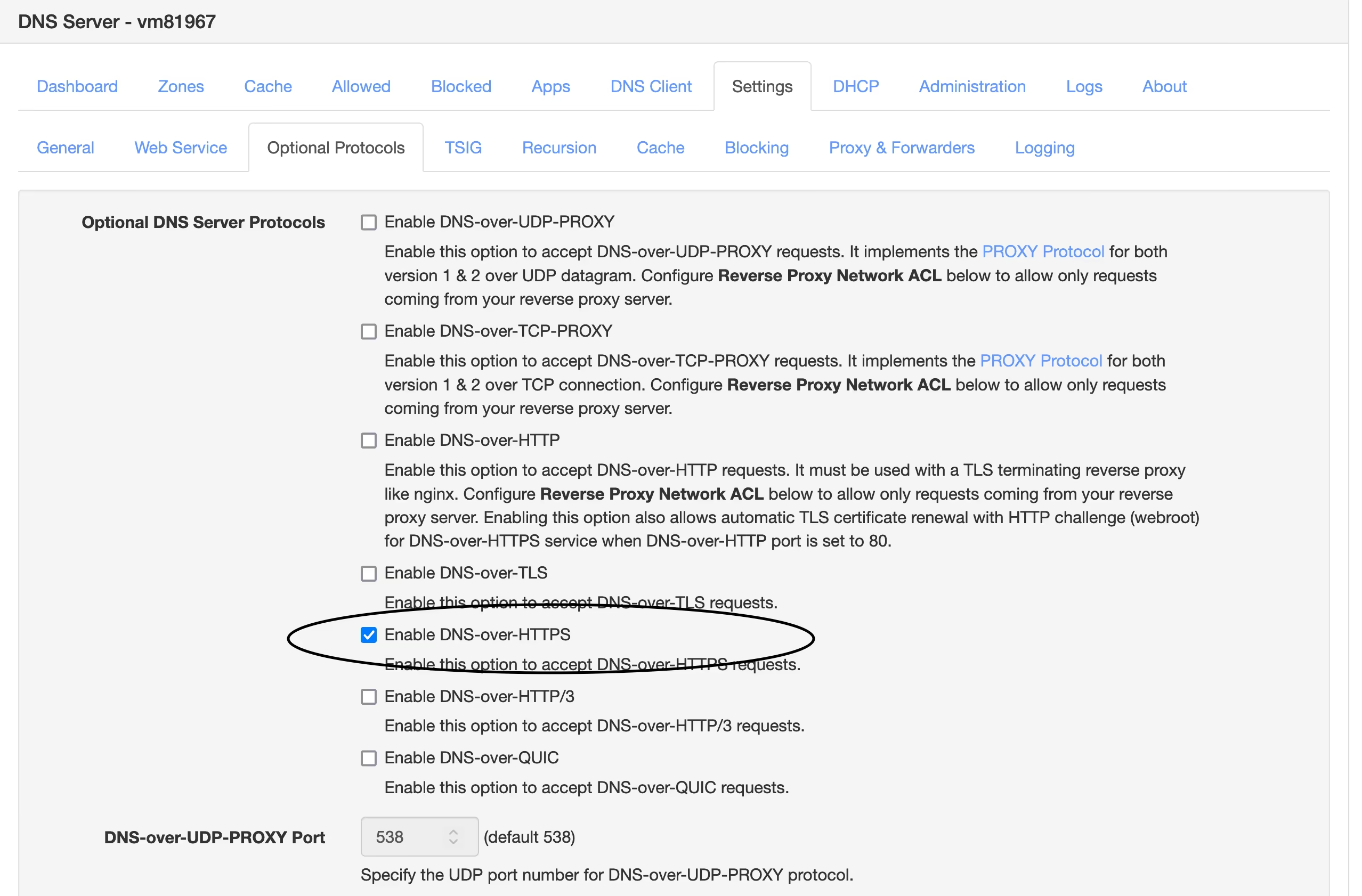 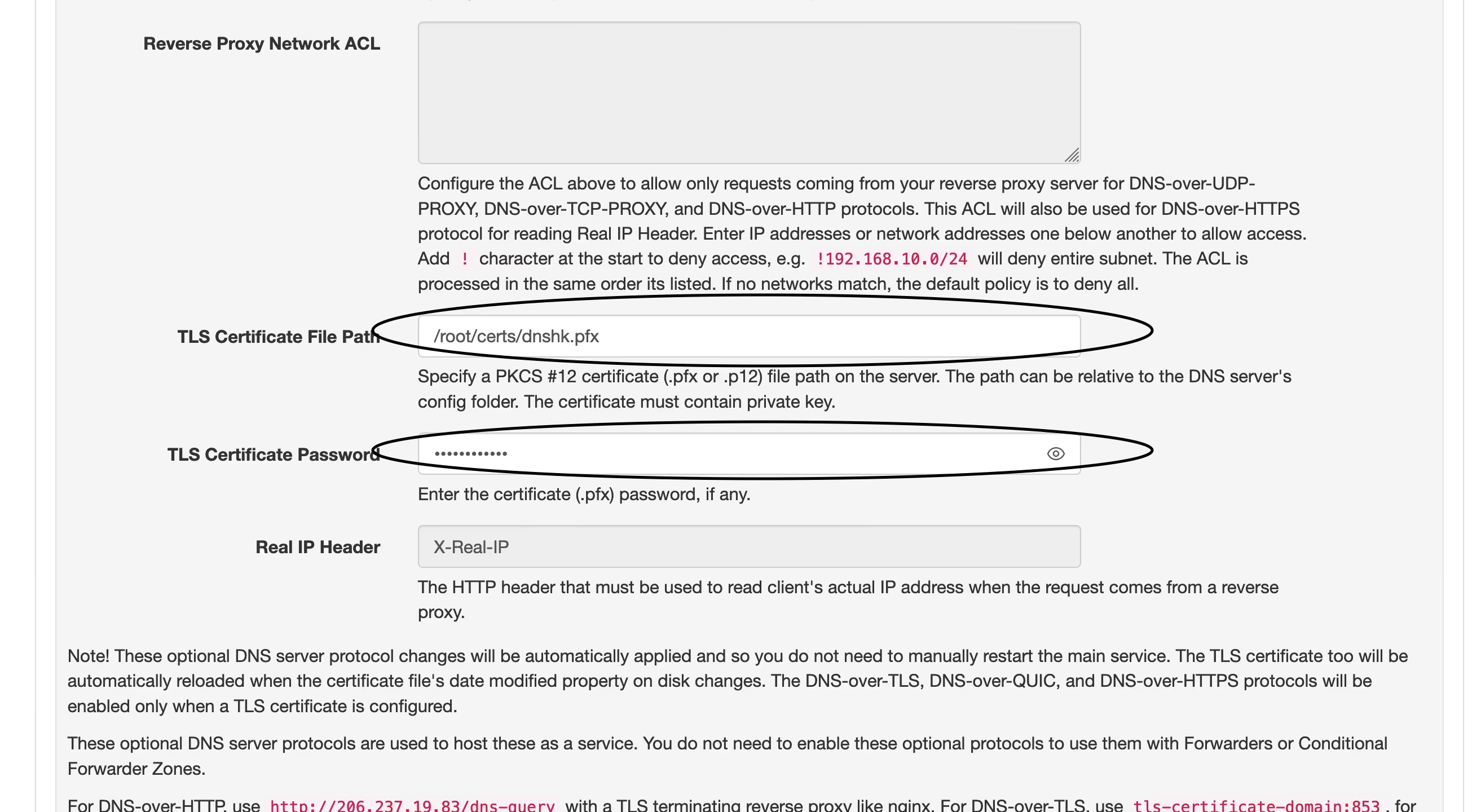 4. 现在打开你的域名,看到如图这样就说明设定成功了,然后在需要设置 DoH 的地方填入 ` https://yourdomain.com/dns-query`即可。 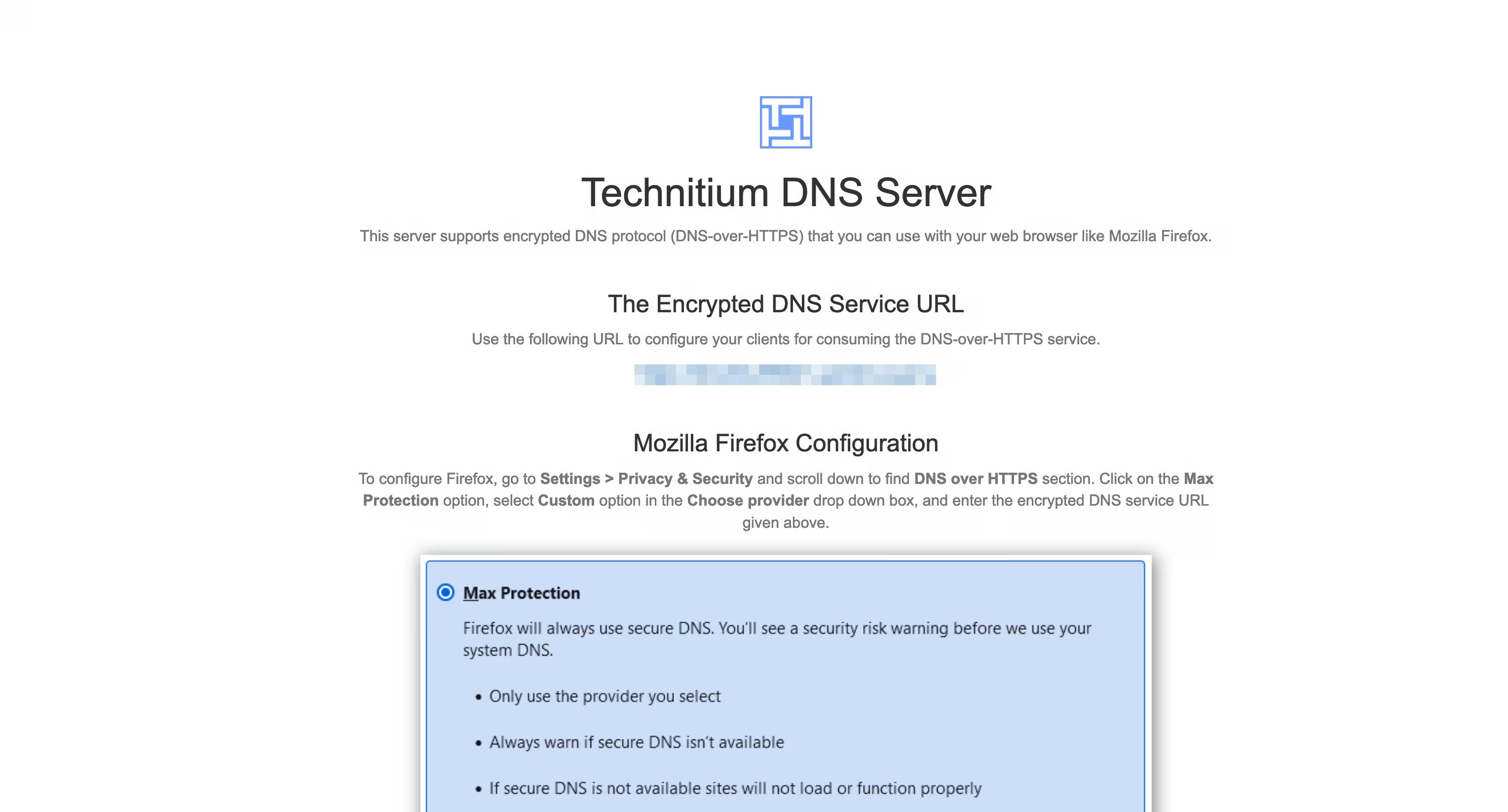 ---- 我在[之前的文章]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)中使用的是 `DNS over HTTP` 并用 Nginx 反代来实现 `DNS over HTTPS` 的,现在直接用 DoH ,省去了配置 Nginx 的部分,只是多了一步证书格式转换,总体上更简单了。 ---- #### 我的设置 - 在`Settings` – `Recursion` 处打开 `Allow Recursion` 以允许递归解析。 - 在`Settings` – `Cache` 处将 `Cache Maximum Entries` 调大些,默认 10000 有点少了。 - 在`Settings` – `General` 处开启 `EDNS Client Subnet (ECS)` 。 - 在`Settings` – `Logging` 处开启 `Use Local Time`。 - 在`Apps` – `App Store` 中安装 `Query Logs (Sqlite)` 以便在 `Logs` – `Query Logs` 处查看 DNS 查询日志。 ##### 以下设置可选 - 在`Settings` – `General` 处开启 `Prefer IPv6` - 在`Settings` – `Web Service` 处为后台管理页面开启 HTTPS,可使用与 DoH 相同的域名和证书,仅端口不同,这个默认 HTTPS 端口是 `53443`。 - 在`Settings` – `Blocking` 处开启拦截功能(默认开启),下面 `Allow / Block List URLs` 可以配置规则,与 AdGuard Home 规则通用,白名单规则须在链接前加上英文叹号 `!`。也可以是本地规则,填路径即可。 - 在`Settings` – `Proxy & Forwarders` 处可以设置上游DNS `Forwarders` 。 @ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
@ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen. @ 378562cd:a6fc6773
2025-04-02 22:41:57Nostr is a decentralized, censorship-resistant social media protocol designed to give users control over online interactions without relying on central authorities. While its architecture offers notable advantages, it also introduces challenges, particularly concerning user anonymity, content moderation, and the dynamics of user influence. Anonymity and the Risk of Bullying Nostr's design allows users to create identities without traditional verification methods like email addresses or phone numbers. Instead, users generate a cryptographic key pair: a public key serving as their identifier and a private key for signing messages. This approach enhances privacy but can lead to the "online disinhibition effect," where individuals feel less accountable for their actions due to perceived anonymity. This phenomenon has been linked to increased instances of cyberbullying, as users may engage in behavior online that they would avoid in face-to-face interactions. Influence Disparities Among Users In decentralized networks like Nostr, users with larger followings can have a more extensive reach, amplifying their messages across the network. This can create disparities where individuals with thousands of followers wield more influence than those with fewer connections. While this dynamic is not unique to Nostr, the protocol's structure may exacerbate the visibility gap between highly followed users and those with a smaller audience. Content Moderation and the Challenge of Deletion Due to Nostr's decentralized nature, content moderation and deletion present significant challenges. Removing content to multiple relays becomes complex once a user posts content to multiple relays, as each relay operates independently. Unlike centralized platforms where a post can be deleted universally, Nostr's architecture means that deleting a post from one relay doesn't ensure its removal from others. This persistence underscores the importance of thoughtful posting, as content may remain accessible indefinitely. Mitigation Strategies and User Empowerment Despite these challenges, Nostr offers mechanisms to empower users to manage their experience. Clients can implement features allowing users to mute or block others, tailoring their interactions and content exposure. Additionally, some clients support user-led moderation, enabling individuals to label content as offensive or inappropriate, contributing to a community-driven approach to content management. In summary, while Nostr's decentralized and anonymous framework promotes freedom and resistance to censorship, it also necessitates a proactive approach from users to navigate challenges related to anonymity, influence disparities, and content permanence. As the platform evolves, ongoing development and community engagement will be crucial in addressing these issues to foster a safe and equitable environment for all participants.
@ 378562cd:a6fc6773
2025-04-02 22:41:57Nostr is a decentralized, censorship-resistant social media protocol designed to give users control over online interactions without relying on central authorities. While its architecture offers notable advantages, it also introduces challenges, particularly concerning user anonymity, content moderation, and the dynamics of user influence. Anonymity and the Risk of Bullying Nostr's design allows users to create identities without traditional verification methods like email addresses or phone numbers. Instead, users generate a cryptographic key pair: a public key serving as their identifier and a private key for signing messages. This approach enhances privacy but can lead to the "online disinhibition effect," where individuals feel less accountable for their actions due to perceived anonymity. This phenomenon has been linked to increased instances of cyberbullying, as users may engage in behavior online that they would avoid in face-to-face interactions. Influence Disparities Among Users In decentralized networks like Nostr, users with larger followings can have a more extensive reach, amplifying their messages across the network. This can create disparities where individuals with thousands of followers wield more influence than those with fewer connections. While this dynamic is not unique to Nostr, the protocol's structure may exacerbate the visibility gap between highly followed users and those with a smaller audience. Content Moderation and the Challenge of Deletion Due to Nostr's decentralized nature, content moderation and deletion present significant challenges. Removing content to multiple relays becomes complex once a user posts content to multiple relays, as each relay operates independently. Unlike centralized platforms where a post can be deleted universally, Nostr's architecture means that deleting a post from one relay doesn't ensure its removal from others. This persistence underscores the importance of thoughtful posting, as content may remain accessible indefinitely. Mitigation Strategies and User Empowerment Despite these challenges, Nostr offers mechanisms to empower users to manage their experience. Clients can implement features allowing users to mute or block others, tailoring their interactions and content exposure. Additionally, some clients support user-led moderation, enabling individuals to label content as offensive or inappropriate, contributing to a community-driven approach to content management. In summary, while Nostr's decentralized and anonymous framework promotes freedom and resistance to censorship, it also necessitates a proactive approach from users to navigate challenges related to anonymity, influence disparities, and content permanence. As the platform evolves, ongoing development and community engagement will be crucial in addressing these issues to foster a safe and equitable environment for all participants. @ 5cf42f9d:4465eebf
2025-04-02 21:32:31
@ 5cf42f9d:4465eebf
2025-04-02 21:32:31 @ ef53426a:7e988851
2025-04-02 21:02:06# Bartering and early money \ Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align. Enter money. It’s used as an indirect exchange for any goods, so everyone wants it. Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services. As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money. --- # Gold — the basis for sound money \ Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining). Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something. Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money. --- # Currencies devalued \ Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire. The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold. In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned. --- # Government-backed money \ Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies. By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate. The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold. --- # Sound money = functioning economy \ Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future. The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events. --- # Recessions and debt arise from unsound money \ Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles. According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt. We need to return to sound money and a new gold standard. Enter bitcoin. --- # Bitcoin is scarce \ Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued. The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward. Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released. That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value. --- # Bitcoin is secure \ The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information. Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power. Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value. --- # Challenges for adoption \ Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value. Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended. Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system. ---  This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading). ‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018. Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop)
@ ef53426a:7e988851
2025-04-02 21:02:06# Bartering and early money \ Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align. Enter money. It’s used as an indirect exchange for any goods, so everyone wants it. Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services. As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money. --- # Gold — the basis for sound money \ Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining). Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something. Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money. --- # Currencies devalued \ Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire. The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold. In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned. --- # Government-backed money \ Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies. By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate. The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold. --- # Sound money = functioning economy \ Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future. The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events. --- # Recessions and debt arise from unsound money \ Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles. According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt. We need to return to sound money and a new gold standard. Enter bitcoin. --- # Bitcoin is scarce \ Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued. The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward. Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released. That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value. --- # Bitcoin is secure \ The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information. Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power. Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value. --- # Challenges for adoption \ Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value. Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended. Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system. ---  This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading). ‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018. Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop) @ b9f4c34d:7d1a0e31
2025-04-02 20:21:49<p> ConfirmingDocumentPaid </p>
@ b9f4c34d:7d1a0e31
2025-04-02 20:21:49<p> ConfirmingDocumentPaid </p> @ 7d33ba57:1b82db35
2025-04-02 19:47:25Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.  ## **🏛️ Top Things to See & Do in Trogir** ### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡** - Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**. - Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**. - Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**. ### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪** - Offers **stunning panoramic views** over Trogir and the Adriatic. - A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery! ### **3️⃣ Visit Kamerlengo Fortress 🏰** - A **15th-century Venetian fortress** with **amazing sea views** from the top. - In summer, it hosts **concerts and cultural events**. ### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊** - A lively waterfront filled with **cafés, restaurants, and luxury yachts**. - Perfect for a **relaxing evening walk** while watching the sunset.  ### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️** - **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities. - **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**. - **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation. ### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️** - A **stunning turquoise bay**, perfect for **swimming and snorkeling**. - Just **a short boat ride from Trogir**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟 - **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi. - **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.  ## **🚗 How to Get to Trogir** ✈️ **By Air:** - **Split Airport (SPU)** is just **10 minutes away**! 🚕 🚘 **By Car:** - **From Split:** ~30 minutes (27 km) - **From Zadar:** ~1.5 hours (130 km) 🚌 **By Bus:** Frequent buses run between **Split and Trogir**. ⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.  ## **💡 Tips for Visiting Trogir** ✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️ ✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅 ✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟 ✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤 ✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷 
@ 7d33ba57:1b82db35
2025-04-02 19:47:25Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.  ## **🏛️ Top Things to See & Do in Trogir** ### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡** - Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**. - Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**. - Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**. ### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪** - Offers **stunning panoramic views** over Trogir and the Adriatic. - A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery! ### **3️⃣ Visit Kamerlengo Fortress 🏰** - A **15th-century Venetian fortress** with **amazing sea views** from the top. - In summer, it hosts **concerts and cultural events**. ### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊** - A lively waterfront filled with **cafés, restaurants, and luxury yachts**. - Perfect for a **relaxing evening walk** while watching the sunset.  ### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️** - **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities. - **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**. - **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation. ### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️** - A **stunning turquoise bay**, perfect for **swimming and snorkeling**. - Just **a short boat ride from Trogir**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟 - **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi. - **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.  ## **🚗 How to Get to Trogir** ✈️ **By Air:** - **Split Airport (SPU)** is just **10 minutes away**! 🚕 🚘 **By Car:** - **From Split:** ~30 minutes (27 km) - **From Zadar:** ~1.5 hours (130 km) 🚌 **By Bus:** Frequent buses run between **Split and Trogir**. ⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.  ## **💡 Tips for Visiting Trogir** ✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️ ✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅 ✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟 ✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤 ✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷  @ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher
@ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher @ b9f4c34d:7d1a0e31
2025-04-02 15:02:59<p> testssss </p>
@ b9f4c34d:7d1a0e31
2025-04-02 15:02:59<p> testssss </p> @ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2>
@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2> @ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p>
@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p> @ 8d34bd24:414be32b
2025-04-02 14:13:03I was reading this passage last night: > …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine} Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself. This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation. > And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28) When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect: > And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine} When one particular man said that he would follow Jesus anywhere, Jesus responded this way. > As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine} Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort. > “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine} Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect. > “**For my thoughts are not your thoughts,\ > neither are your ways my ways**,”\ > declares the Lord. > > “As the heavens are higher than the earth,\ > so are **my ways higher than your ways**\ > and my thoughts than your thoughts. > > As the rain and the snow\ > come down from heaven,\ > and do not return to it\ > without watering the earth\ > and making it bud and flourish,\ > so that it yields seed for the sower and bread for the eater,\ > so is **my word that goes out from my mouth:\ > It will not return to me empty,\ > but will accomplish what I desire\ > and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine} God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us. > Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine} In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word. > They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine} Peter specifically warns believers to expect trials and hardship. > Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And, > > “If it is hard for the righteous to be saved,\ > what will become of the ungodly and the sinner?” > > So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine} Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship. > …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine} No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good. > Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written, > > “For Your sake we are being put to death all day long;\ > We were considered as sheep to be slaughtered.” > ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine} I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be. First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard. Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion. In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before. When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good. We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness. > Oh, the depth of the riches of the wisdom and knowledge of God!\ > How unsearchable his judgments,\ > and his paths beyond tracing out!\ > “Who has known the mind of the Lord?\ > Or who has been his counselor?”\ > “Who has ever given to God,\ > that God should repay them?”\ > For from him and through him and for him are all things.\ > To him be the glory forever! Amen. (Romans 11:33-36) Trust Jesus
@ 8d34bd24:414be32b
2025-04-02 14:13:03I was reading this passage last night: > …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine} Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself. This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation. > And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28) When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect: > And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine} When one particular man said that he would follow Jesus anywhere, Jesus responded this way. > As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine} Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort. > “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine} Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect. > “**For my thoughts are not your thoughts,\ > neither are your ways my ways**,”\ > declares the Lord. > > “As the heavens are higher than the earth,\ > so are **my ways higher than your ways**\ > and my thoughts than your thoughts. > > As the rain and the snow\ > come down from heaven,\ > and do not return to it\ > without watering the earth\ > and making it bud and flourish,\ > so that it yields seed for the sower and bread for the eater,\ > so is **my word that goes out from my mouth:\ > It will not return to me empty,\ > but will accomplish what I desire\ > and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine} God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us. > Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine} In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word. > They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine} Peter specifically warns believers to expect trials and hardship. > Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And, > > “If it is hard for the righteous to be saved,\ > what will become of the ungodly and the sinner?” > > So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine} Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship. > …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine} No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good. > Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written, > > “For Your sake we are being put to death all day long;\ > We were considered as sheep to be slaughtered.” > ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine} I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be. First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard. Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion. In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before. When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good. We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness. > Oh, the depth of the riches of the wisdom and knowledge of God!\ > How unsearchable his judgments,\ > and his paths beyond tracing out!\ > “Who has known the mind of the Lord?\ > Or who has been his counselor?”\ > “Who has ever given to God,\ > that God should repay them?”\ > For from him and through him and for him are all things.\ > To him be the glory forever! Amen. (Romans 11:33-36) Trust Jesus @ 06639a38:655f8f71
2025-04-02 13:47:57You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github. Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits. Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19) ### **TLV's** Things were getting more complicated with the other prefixes / identifiers defined in NIP-19: * `nevent` * `naddr` * `nprofile` This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's. _When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._ _For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._ These possible standardized `TLV` types are: * `0`_:_ `special` * _depends on the bech32 prefix:_ * _for_ `nprofile` _it will be the 32 bytes of the profile public key_ * _for_ `nevent` _it will be the 32 bytes of the event id_ * _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._ * `1`_:_ `relay` * _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_ * _this may be included multiple times_ * `2`_:_ `author` * _for_ `naddr`_, the 32 bytes of the pubkey of the event_ * _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_ * `3`_:_ `kind` * _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_ * _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_ These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters. Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code): * [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74) * [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19) ### **So what's next?** * NIP-19 code housekeeping + refactoring * Prepare a new release with NIP-19 integration * Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev)
@ 06639a38:655f8f71
2025-04-02 13:47:57You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github. Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits. Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19) ### **TLV's** Things were getting more complicated with the other prefixes / identifiers defined in NIP-19: * `nevent` * `naddr` * `nprofile` This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's. _When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._ _For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._ These possible standardized `TLV` types are: * `0`_:_ `special` * _depends on the bech32 prefix:_ * _for_ `nprofile` _it will be the 32 bytes of the profile public key_ * _for_ `nevent` _it will be the 32 bytes of the event id_ * _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._ * `1`_:_ `relay` * _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_ * _this may be included multiple times_ * `2`_:_ `author` * _for_ `naddr`_, the 32 bytes of the pubkey of the event_ * _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_ * `3`_:_ `kind` * _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_ * _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_ These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters. Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code): * [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74) * [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19) ### **So what's next?** * NIP-19 code housekeeping + refactoring * Prepare a new release with NIP-19 integration * Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev) @ 7bdef7be:784a5805
2025-04-02 12:37:35The following script try, using [nak](https://github.com/fiatjaf/nak), to find out the last ten people who have followed a `target_pubkey`, sorted by the most recent. It's possibile to shorten `search_timerange` to speed up the search. ``` #!/usr/bin/env fish # Target pubkey we're looking for in the tags set target_pubkey "6e468422dfb74a5738702a8823b9b28168abab8655faacb6853cd0ee15deee93" set current_time (date +%s) set search_timerange (math $current_time - 600) # 24 hours = 86400 seconds set pubkeys (nak req --kind 3 -s $search_timerange wss://relay.damus.io/ wss://nos.lol/ 2>/dev/null | \ jq -r --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[] | select(.[0] == "p" and .[1] == $target)) | .pubkey ' | sort -u) if test -z "$pubkeys" exit 1 end set all_events "" set extended_search_timerange (math $current_time - 31536000) # One year for pubkey in $pubkeys echo "Checking $pubkey" set events (nak req --author $pubkey -l 5 -k 3 -s $extended_search_timerange wss://relay.damus.io wss://nos.lol 2>/dev/null | \ jq -c --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[][] == $target) ' 2>/dev/null) set count (echo "$events" | jq -s 'length') if test "$count" -eq 1 set all_events $all_events $events end end if test -n "$all_events" echo -e "Last people following $target_pubkey:" echo -e "" set sorted_events (printf "%s\n" $all_events | jq -r -s ' unique_by(.id) | sort_by(-.created_at) | .[] | @json ') for event in $sorted_events set npub (echo $event | jq -r '.pubkey' | nak encode npub) set created_at (echo $event | jq -r '.created_at') if test (uname) = "Darwin" set follow_date (date -r "$created_at" "+%Y-%m-%d %H:%M") else set follow_date (date -d @"$created_at" "+%Y-%m-%d %H:%M") end echo "$follow_date - $npub" end end ```
@ 7bdef7be:784a5805
2025-04-02 12:37:35The following script try, using [nak](https://github.com/fiatjaf/nak), to find out the last ten people who have followed a `target_pubkey`, sorted by the most recent. It's possibile to shorten `search_timerange` to speed up the search. ``` #!/usr/bin/env fish # Target pubkey we're looking for in the tags set target_pubkey "6e468422dfb74a5738702a8823b9b28168abab8655faacb6853cd0ee15deee93" set current_time (date +%s) set search_timerange (math $current_time - 600) # 24 hours = 86400 seconds set pubkeys (nak req --kind 3 -s $search_timerange wss://relay.damus.io/ wss://nos.lol/ 2>/dev/null | \ jq -r --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[] | select(.[0] == "p" and .[1] == $target)) | .pubkey ' | sort -u) if test -z "$pubkeys" exit 1 end set all_events "" set extended_search_timerange (math $current_time - 31536000) # One year for pubkey in $pubkeys echo "Checking $pubkey" set events (nak req --author $pubkey -l 5 -k 3 -s $extended_search_timerange wss://relay.damus.io wss://nos.lol 2>/dev/null | \ jq -c --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[][] == $target) ' 2>/dev/null) set count (echo "$events" | jq -s 'length') if test "$count" -eq 1 set all_events $all_events $events end end if test -n "$all_events" echo -e "Last people following $target_pubkey:" echo -e "" set sorted_events (printf "%s\n" $all_events | jq -r -s ' unique_by(.id) | sort_by(-.created_at) | .[] | @json ') for event in $sorted_events set npub (echo $event | jq -r '.pubkey' | nak encode npub) set created_at (echo $event | jq -r '.created_at') if test (uname) = "Darwin" set follow_date (date -r "$created_at" "+%Y-%m-%d %H:%M") else set follow_date (date -d @"$created_at" "+%Y-%m-%d %H:%M") end echo "$follow_date - $npub" end end ``` @ fd06f542:8d6d54cd
2025-04-02 12:34:07- [首页](/readme.md) - [国内开发者](/01.md)
@ fd06f542:8d6d54cd
2025-04-02 12:34:07- [首页](/readme.md) - [国内开发者](/01.md) @ 7bdef7be:784a5805
2025-04-02 12:12:12We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so **everyone can actually snoop what we are interested in**, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: **encrypted lists**. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, **we can hide the lists' content from others**. The implications are obvious: we can not only have a more organized way to browse content, but it is also **really private one**. One might wonder what use can really be made of private lists; here are some examples: * Browse “can't miss” content from users I consider a priority; * Supervise competitors or adversarial parts; * Monitor sensible topics (tags); * Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of **how many bots scan our actions to profile us**. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an **easier option** to start offering private lists: give the user **the possibility to simply mark them as local-only**, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage **both encrypted and local-only lists**. Beg your Nostr client to implement private lists!
@ 7bdef7be:784a5805
2025-04-02 12:12:12We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so **everyone can actually snoop what we are interested in**, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: **encrypted lists**. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, **we can hide the lists' content from others**. The implications are obvious: we can not only have a more organized way to browse content, but it is also **really private one**. One might wonder what use can really be made of private lists; here are some examples: * Browse “can't miss” content from users I consider a priority; * Supervise competitors or adversarial parts; * Monitor sensible topics (tags); * Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of **how many bots scan our actions to profile us**. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an **easier option** to start offering private lists: give the user **the possibility to simply mark them as local-only**, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage **both encrypted and local-only lists**. Beg your Nostr client to implement private lists! @ 04cb16e4:2ec3e5d5
2025-04-02 10:51:31Wenn irgendein weltpolitisches Thema auf den Tisch kommt, wird zumeist erst einmal gefragt, ob du dafür oder dagegen bist und auf welcher Seite du dich befindest. Das macht es einfacher, dich als Freund oder Feind einzusortieren. So wird das Leben übersichtlicher und man muss nicht in die Tiefe gehen und sich mit lästigen Details auseinandersetzen. Man muss auch nicht verreisen um sich ein Bild zu machen. Dafür gibt es ja die Tagesschau. Klassisches Beispiel: Ich war vor Kurzem mit einigen Freunden essen. Einer berichtete entsetzt: „Der Putin hat die Heimatstadt von Selenski angegriffen!“  Ich versuchte mir das bildlich vorzustellen und kam zu dem Schluss, das „der Putin“ wahrscheinlich Verstärkung dabei hatte. Und ausgerechnet nachdem Trump und dessen Flügelmann Vance den armen Wolodymyr rund gemacht hatten, greift der böse Imperator dessen Heimatstadt an. Das ist fies! Das macht „der Putin“ wahrscheinlich immer so, wenn er jemandem eins auswischen will. Die Heimatstadt angreifen! Ganz gleich, ob es strategisch gerade Sinn macht oder nicht. "Der Putin" ist halt ein Teufel. [Telegramkanal RBM](https://t.me/radio_berliner_morgenroete_de) [Radio Berliner Morgenröte auf X](https://x.com/RBM_Schindler) Ich denke viele gucken einfach zu viele qualitativ minderwertige Spielfilme und können Fiktion und Realität nicht mehr voneinander unterscheiden. Möglicherweise meinen sie auch, weil sie die Handlung eines Kriegsfilmes gerafft haben, verstehen sie einen Krieg. <https://www.eisbrenner.de/produkt-kategorie/buch/> <https://befreiung.org/> Mein Gesprächspartner Tino Eisbrenner hat keine Sightseeing Tour durch Moskau gemacht, sondern ist in Land und Leute regelrecht eingetaucht. Außerdem kommt seine Schwiegermutter aus Russland. Da ist man dem ganzen auch menschlich viel näher und bekommt man ganz andere Einblicke als die, die einem von der Tagesschau gewährt werden. Tino ist als Friedensmusiker viel im Osten unterwegs, unter anderem auch in Georgien, Weißrussland und auf der Krim. Er spricht mit Politikern, Künstlern, Journalisten, Taxifahrern und Dissidenten. Und viele fragen ihn: „Was ist eigentlich mit den Deutschen los?“ Gute Frage! Was ist eigentlich mit uns los? Wir senden unsere Volksvertreter in die Welt hinaus, damit sie Staatsoberhäuptern aus Ländern - die um ein Vielfaches umfangreicher an Fläche und Einwohnerzahl sind und eine komplett andere Kulturgeschichte haben - damit sie denen erklären können wie man seinen Job macht. Wahrscheinlich in dem irrwitzigen Glauben, dass sie selbst ihren Job tadellos und vorbildlich ausführen. **Spenden nehmen wir entweder mit dem Paypal Button am Ende** **[unserer Webseite](https://radio-berliner-morgenroete.de/)** **<https://radio-berliner-morgenroete.de/>** **oder per Überweisung aufs Bankkonto: DE93 1001 1001 2624 3740 74 entgegen.** Wir sind aber nicht nur verantwortlich für unsere politische Führung, sondern auch für unseren Umgang miteinander. Denn im „Großen“ gilt dasselbe wie im „Kleinen“! Man sollte erst mal bei sich selbst schauen wo es hakt und dann miteinander ins Gespräch gehen. Der Mangel an Realitätssinn und Konfliktfähigkeit zieht sich durch alle Schichten unserer Bevölkerung. Deswegen sagt Radio Berliner Morgenröte: „Wenn ihr Frieden wollt, fangt in Deutschland an und wenn ihr euch eine Meinung über Russland oder China bilden wollt, dann fahrt einfach mal dorthin und redet mit den Leuten, So wie Tino. Mir hat es riesig Spaß gemacht, ihm zuzuhören. Weiterer Buchtipp – [Ausgegendert](https://www.masselverlag.de/v/yHj2uBdfbu/) <https://mcdn.podbean.com/mf/web/e5qbg23gz6mru9zz/Tino_Eisbrenner9tbpx.mp3>
@ 04cb16e4:2ec3e5d5
2025-04-02 10:51:31Wenn irgendein weltpolitisches Thema auf den Tisch kommt, wird zumeist erst einmal gefragt, ob du dafür oder dagegen bist und auf welcher Seite du dich befindest. Das macht es einfacher, dich als Freund oder Feind einzusortieren. So wird das Leben übersichtlicher und man muss nicht in die Tiefe gehen und sich mit lästigen Details auseinandersetzen. Man muss auch nicht verreisen um sich ein Bild zu machen. Dafür gibt es ja die Tagesschau. Klassisches Beispiel: Ich war vor Kurzem mit einigen Freunden essen. Einer berichtete entsetzt: „Der Putin hat die Heimatstadt von Selenski angegriffen!“  Ich versuchte mir das bildlich vorzustellen und kam zu dem Schluss, das „der Putin“ wahrscheinlich Verstärkung dabei hatte. Und ausgerechnet nachdem Trump und dessen Flügelmann Vance den armen Wolodymyr rund gemacht hatten, greift der böse Imperator dessen Heimatstadt an. Das ist fies! Das macht „der Putin“ wahrscheinlich immer so, wenn er jemandem eins auswischen will. Die Heimatstadt angreifen! Ganz gleich, ob es strategisch gerade Sinn macht oder nicht. "Der Putin" ist halt ein Teufel. [Telegramkanal RBM](https://t.me/radio_berliner_morgenroete_de) [Radio Berliner Morgenröte auf X](https://x.com/RBM_Schindler) Ich denke viele gucken einfach zu viele qualitativ minderwertige Spielfilme und können Fiktion und Realität nicht mehr voneinander unterscheiden. Möglicherweise meinen sie auch, weil sie die Handlung eines Kriegsfilmes gerafft haben, verstehen sie einen Krieg. <https://www.eisbrenner.de/produkt-kategorie/buch/> <https://befreiung.org/> Mein Gesprächspartner Tino Eisbrenner hat keine Sightseeing Tour durch Moskau gemacht, sondern ist in Land und Leute regelrecht eingetaucht. Außerdem kommt seine Schwiegermutter aus Russland. Da ist man dem ganzen auch menschlich viel näher und bekommt man ganz andere Einblicke als die, die einem von der Tagesschau gewährt werden. Tino ist als Friedensmusiker viel im Osten unterwegs, unter anderem auch in Georgien, Weißrussland und auf der Krim. Er spricht mit Politikern, Künstlern, Journalisten, Taxifahrern und Dissidenten. Und viele fragen ihn: „Was ist eigentlich mit den Deutschen los?“ Gute Frage! Was ist eigentlich mit uns los? Wir senden unsere Volksvertreter in die Welt hinaus, damit sie Staatsoberhäuptern aus Ländern - die um ein Vielfaches umfangreicher an Fläche und Einwohnerzahl sind und eine komplett andere Kulturgeschichte haben - damit sie denen erklären können wie man seinen Job macht. Wahrscheinlich in dem irrwitzigen Glauben, dass sie selbst ihren Job tadellos und vorbildlich ausführen. **Spenden nehmen wir entweder mit dem Paypal Button am Ende** **[unserer Webseite](https://radio-berliner-morgenroete.de/)** **<https://radio-berliner-morgenroete.de/>** **oder per Überweisung aufs Bankkonto: DE93 1001 1001 2624 3740 74 entgegen.** Wir sind aber nicht nur verantwortlich für unsere politische Führung, sondern auch für unseren Umgang miteinander. Denn im „Großen“ gilt dasselbe wie im „Kleinen“! Man sollte erst mal bei sich selbst schauen wo es hakt und dann miteinander ins Gespräch gehen. Der Mangel an Realitätssinn und Konfliktfähigkeit zieht sich durch alle Schichten unserer Bevölkerung. Deswegen sagt Radio Berliner Morgenröte: „Wenn ihr Frieden wollt, fangt in Deutschland an und wenn ihr euch eine Meinung über Russland oder China bilden wollt, dann fahrt einfach mal dorthin und redet mit den Leuten, So wie Tino. Mir hat es riesig Spaß gemacht, ihm zuzuhören. Weiterer Buchtipp – [Ausgegendert](https://www.masselverlag.de/v/yHj2uBdfbu/) <https://mcdn.podbean.com/mf/web/e5qbg23gz6mru9zz/Tino_Eisbrenner9tbpx.mp3> @ d04ecf33:1d62aa90
2025-04-02 09:48:16## Physical prototyping 3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes. Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations. ## Prototypers of Ideas Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop. However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car. From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase. And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc. So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better. ## Economic Impact 3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare. Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away. ## Progress LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators. If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today. If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences. Keep printing ideas and execute on them! Learn and repeat. The path to success. #llm #ai #agi #3dp #programming
@ d04ecf33:1d62aa90
2025-04-02 09:48:16## Physical prototyping 3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes. Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations. ## Prototypers of Ideas Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop. However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car. From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase. And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc. So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better. ## Economic Impact 3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare. Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away. ## Progress LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators. If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today. If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences. Keep printing ideas and execute on them! Learn and repeat. The path to success. #llm #ai #agi #3dp #programming @ 7d33ba57:1b82db35
2025-04-02 08:15:08Supetar is the main town and ferry port on Brač Island, located just across the sea from Split. It’s a charming coastal town with historic streets, beautiful beaches, and a relaxed island vibe. As the main entry point to Brač, it’s the perfect base for exploring the island’s stunning beaches, olive groves, and cultural landmarks.  ## **🏛️ Top Things to See & Do in Supetar** ### **1️⃣ Explore the Supetar Old Town 🏡** - Stroll through **narrow, stone-paved alleys**, lined with **historic buildings and seaside cafés**. - Visit **St. Peter’s Church & Mausoleum**, featuring intricate stone carvings. - Admire the **harbor filled with fishing boats**, offering postcard-worthy views. ### **2️⃣ Relax on Supetar’s Beaches 🏖️** - **Banj Beach** – A **family-friendly beach** with crystal-clear water & soft pebbles. - **Acapulco Beach** – A more secluded, **rocky beach with turquoise waters**. - **Vela Luka Bay** – A beautiful bay **surrounded by pine forests**, perfect for relaxation. ### **3️⃣ Visit the Olive Oil Museum in Škrip 🫒** - **Just 15 minutes from Supetar**, this museum showcases **Brač’s olive oil heritage**. - Try traditional **Dalmatian olive oil tastings** & local island delicacies.  ### **4️⃣ Take a Boat Trip to the Famous Zlatni Rat Beach ⛵** - One of **Croatia’s most iconic beaches**, known for its **shifting horn-shaped coastline**. - Located in **Bol**, just a short boat or car ride away from Supetar. ### **5️⃣ Hike or Drive to Vidova Gora 🌄** - The **highest peak on the Adriatic islands (778m)**, offering **breathtaking views** over Brač, Hvar, and beyond. - Accessible by **hiking (moderate difficulty) or driving**.  ### **6️⃣ Try Dalmatian Cuisine 🍽️** - **Vitalac** – A unique Brač specialty, made from lamb offal and cooked over an open fire. - **Pašticada** – A slow-cooked beef dish, traditionally served with gnocchi. - **Homemade Brač cheese & wine** – Try local goat cheese paired with **Plavac Mali wine**.  ## **🚗 How to Get to Supetar** ⛴️ **By Ferry (from Split):** - The **Split-Supetar ferry** is the **main connection** (50 min ride). - Ferries run **frequently** (especially in summer). 🚘 **By Car:** - **Supetar is the best entry point for road trips across Brač**. - Car rentals are available in town or at the ferry port.  ## **💡 Tips for Visiting Supetar** ✅ **Best time to visit?** **May–September** for warm weather & clear seas ☀️ ✅ **Stay at least a night** – Supetar has a lovely evening atmosphere 🌙 ✅ **Rent a scooter or car** to explore Brač’s hidden beaches & inland villages 🏍️ ✅ **Try local wines & olive oils** – Brač is famous for both 🍷🫒 ✅ **Visit early in the morning** for a peaceful experience before ferries get busy ⏳ 
@ 7d33ba57:1b82db35
2025-04-02 08:15:08Supetar is the main town and ferry port on Brač Island, located just across the sea from Split. It’s a charming coastal town with historic streets, beautiful beaches, and a relaxed island vibe. As the main entry point to Brač, it’s the perfect base for exploring the island’s stunning beaches, olive groves, and cultural landmarks.  ## **🏛️ Top Things to See & Do in Supetar** ### **1️⃣ Explore the Supetar Old Town 🏡** - Stroll through **narrow, stone-paved alleys**, lined with **historic buildings and seaside cafés**. - Visit **St. Peter’s Church & Mausoleum**, featuring intricate stone carvings. - Admire the **harbor filled with fishing boats**, offering postcard-worthy views. ### **2️⃣ Relax on Supetar’s Beaches 🏖️** - **Banj Beach** – A **family-friendly beach** with crystal-clear water & soft pebbles. - **Acapulco Beach** – A more secluded, **rocky beach with turquoise waters**. - **Vela Luka Bay** – A beautiful bay **surrounded by pine forests**, perfect for relaxation. ### **3️⃣ Visit the Olive Oil Museum in Škrip 🫒** - **Just 15 minutes from Supetar**, this museum showcases **Brač’s olive oil heritage**. - Try traditional **Dalmatian olive oil tastings** & local island delicacies.  ### **4️⃣ Take a Boat Trip to the Famous Zlatni Rat Beach ⛵** - One of **Croatia’s most iconic beaches**, known for its **shifting horn-shaped coastline**. - Located in **Bol**, just a short boat or car ride away from Supetar. ### **5️⃣ Hike or Drive to Vidova Gora 🌄** - The **highest peak on the Adriatic islands (778m)**, offering **breathtaking views** over Brač, Hvar, and beyond. - Accessible by **hiking (moderate difficulty) or driving**.  ### **6️⃣ Try Dalmatian Cuisine 🍽️** - **Vitalac** – A unique Brač specialty, made from lamb offal and cooked over an open fire. - **Pašticada** – A slow-cooked beef dish, traditionally served with gnocchi. - **Homemade Brač cheese & wine** – Try local goat cheese paired with **Plavac Mali wine**.  ## **🚗 How to Get to Supetar** ⛴️ **By Ferry (from Split):** - The **Split-Supetar ferry** is the **main connection** (50 min ride). - Ferries run **frequently** (especially in summer). 🚘 **By Car:** - **Supetar is the best entry point for road trips across Brač**. - Car rentals are available in town or at the ferry port.  ## **💡 Tips for Visiting Supetar** ✅ **Best time to visit?** **May–September** for warm weather & clear seas ☀️ ✅ **Stay at least a night** – Supetar has a lovely evening atmosphere 🌙 ✅ **Rent a scooter or car** to explore Brač’s hidden beaches & inland villages 🏍️ ✅ **Try local wines & olive oils** – Brač is famous for both 🍷🫒 ✅ **Visit early in the morning** for a peaceful experience before ferries get busy ⏳ 