-

@ 1c19eb1a:e22fb0bc
2025-03-03 19:14:42
After my first major review of [Primal on Android](https://www.nostr-reviews.com/post/1733635103705/), we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client.
Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity.
It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub.
If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings.
Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in [NIP-55](https://github.com/nostr-protocol/nips/blob/master/55.md). Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber.
This review of Amber is current as of version 3.2.5.
## Overall Impression
Score: **4.5** / 5
I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec.
Despite being the only well-established Android signer available for Android, Amber ***can*** be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method ([NIP-07](https://github.com/nostr-protocol/nips/blob/master/07.md)) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing.
A running list I created of applications that support login and signing with Amber can be found here: [Nostr Clients with External Signer Support](nostr:naddr1qvzqqqrcvgpzpde8f55w86vrhaeqmd955y4rraw8aunzxgxstsj7eyzgntyev2xtqydhwumn8ghj7un9d3shjtnzwf5kw6r5vfhkcapwdejhgtcpr4mhxue69uhkg6ttv95k7ue3x5cnwtnwdaehgu339e3k7mf0qq4xummnw3ez6cmvd9jkuarn94mkjarg94jhsar9wfhxzmpdwd5kwmn9wgkhxatswphhyaqrcy76t)
I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either [NIP-55](https://github.com/nostr-protocol/nips/blob/master/55.md) or [NIP-46](https://github.com/nostr-protocol/nips/blob/master/46.md) login.
I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn.
nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v
The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time.
## Features
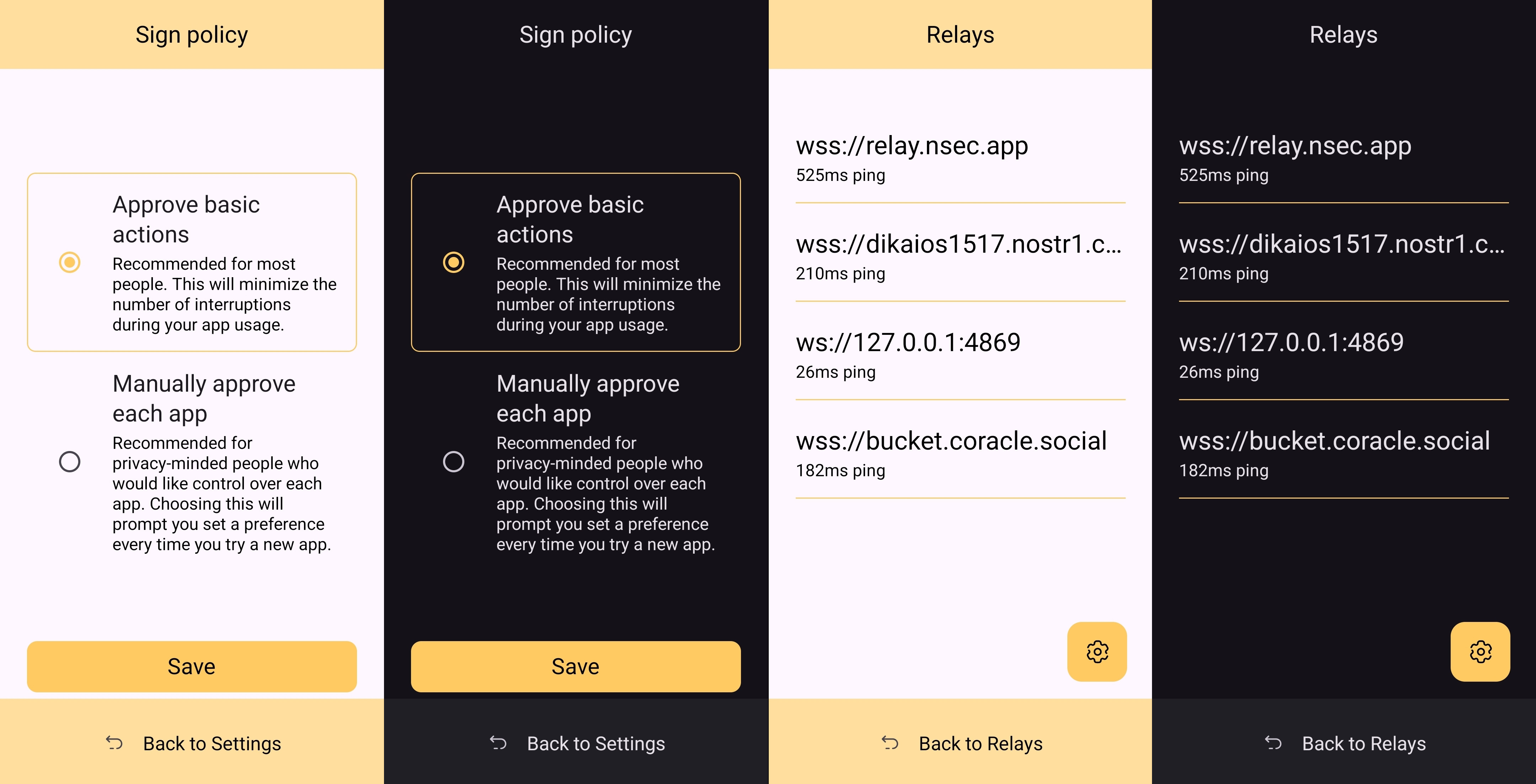
Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control.
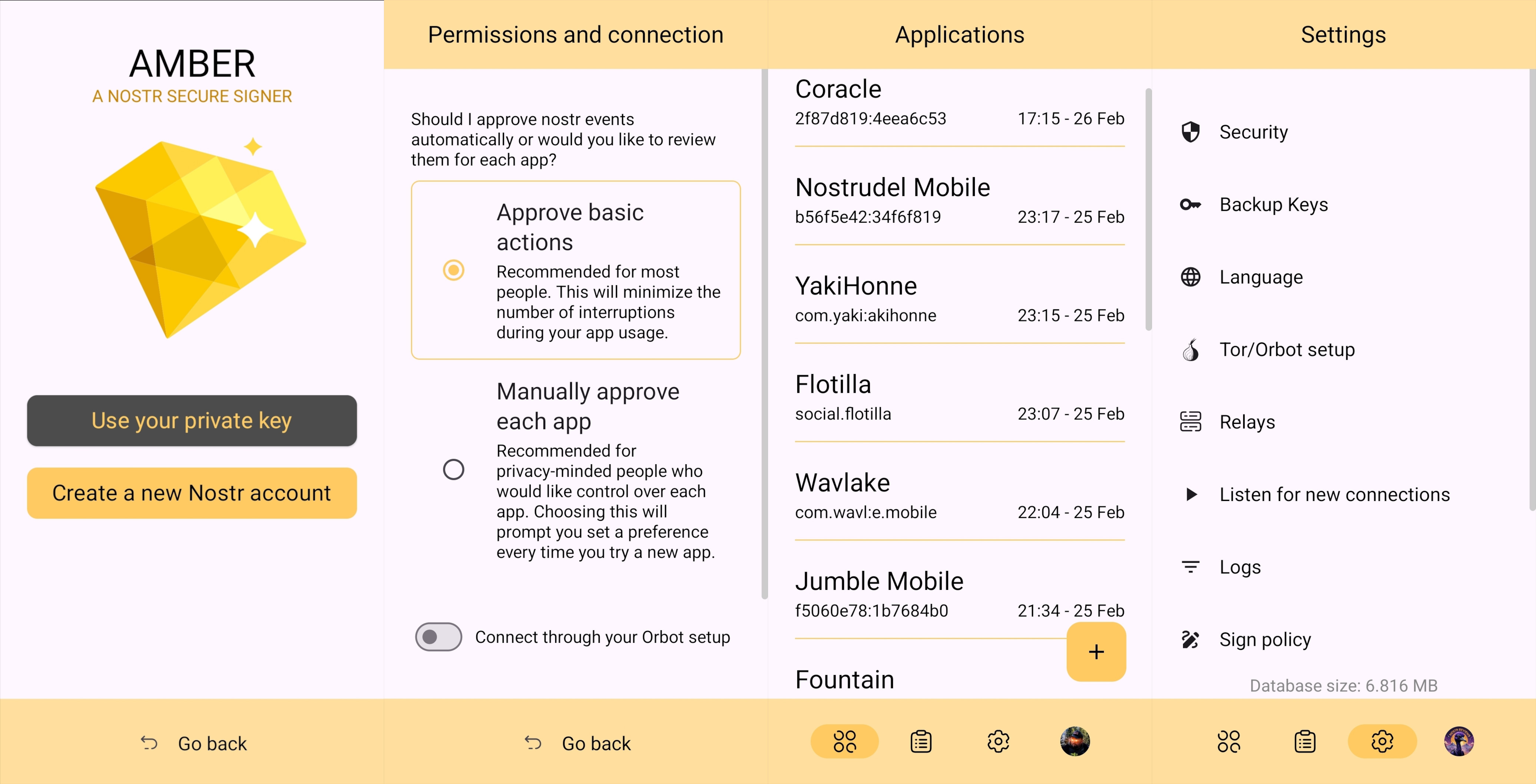
### Android Signing
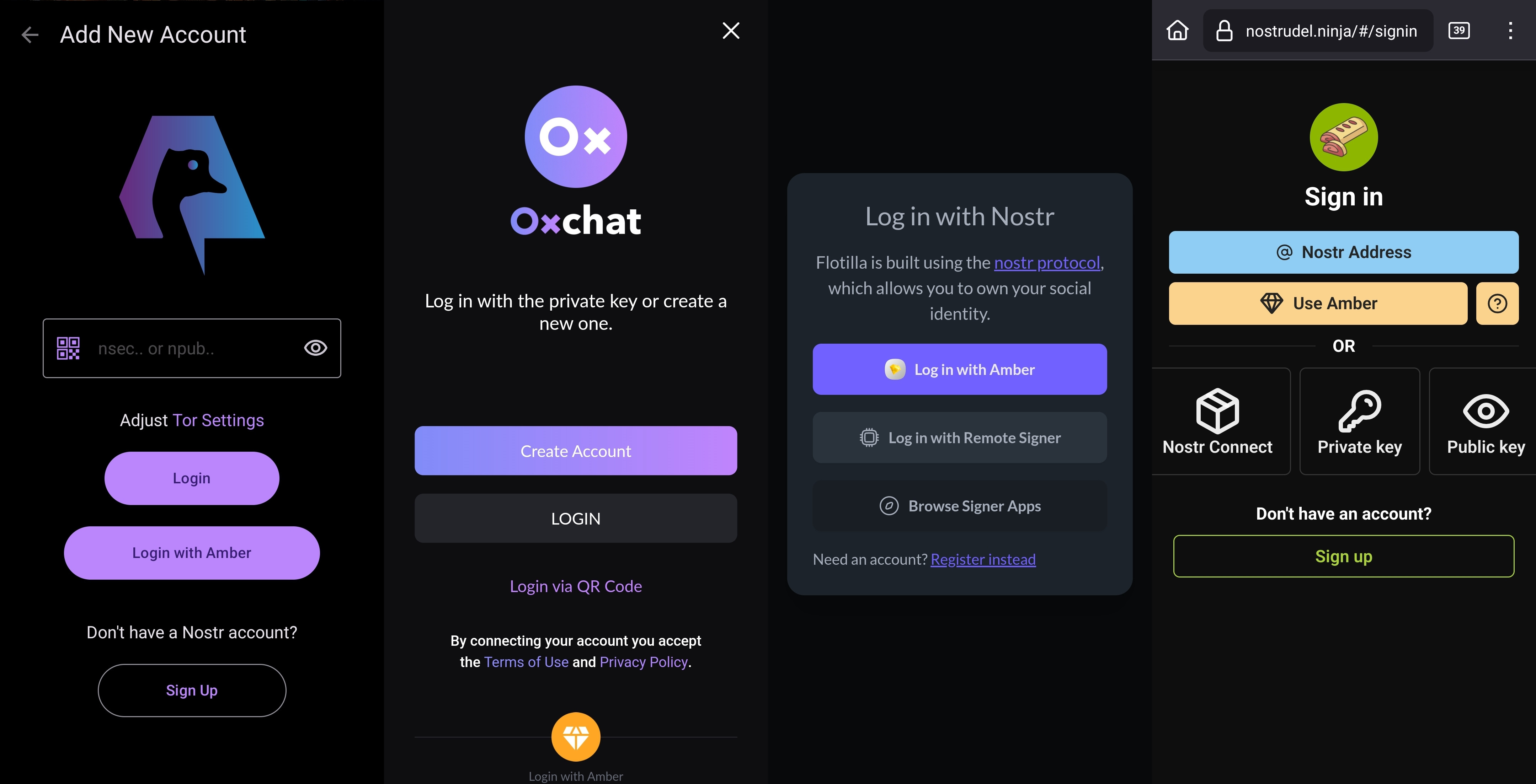
This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in.
This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time.
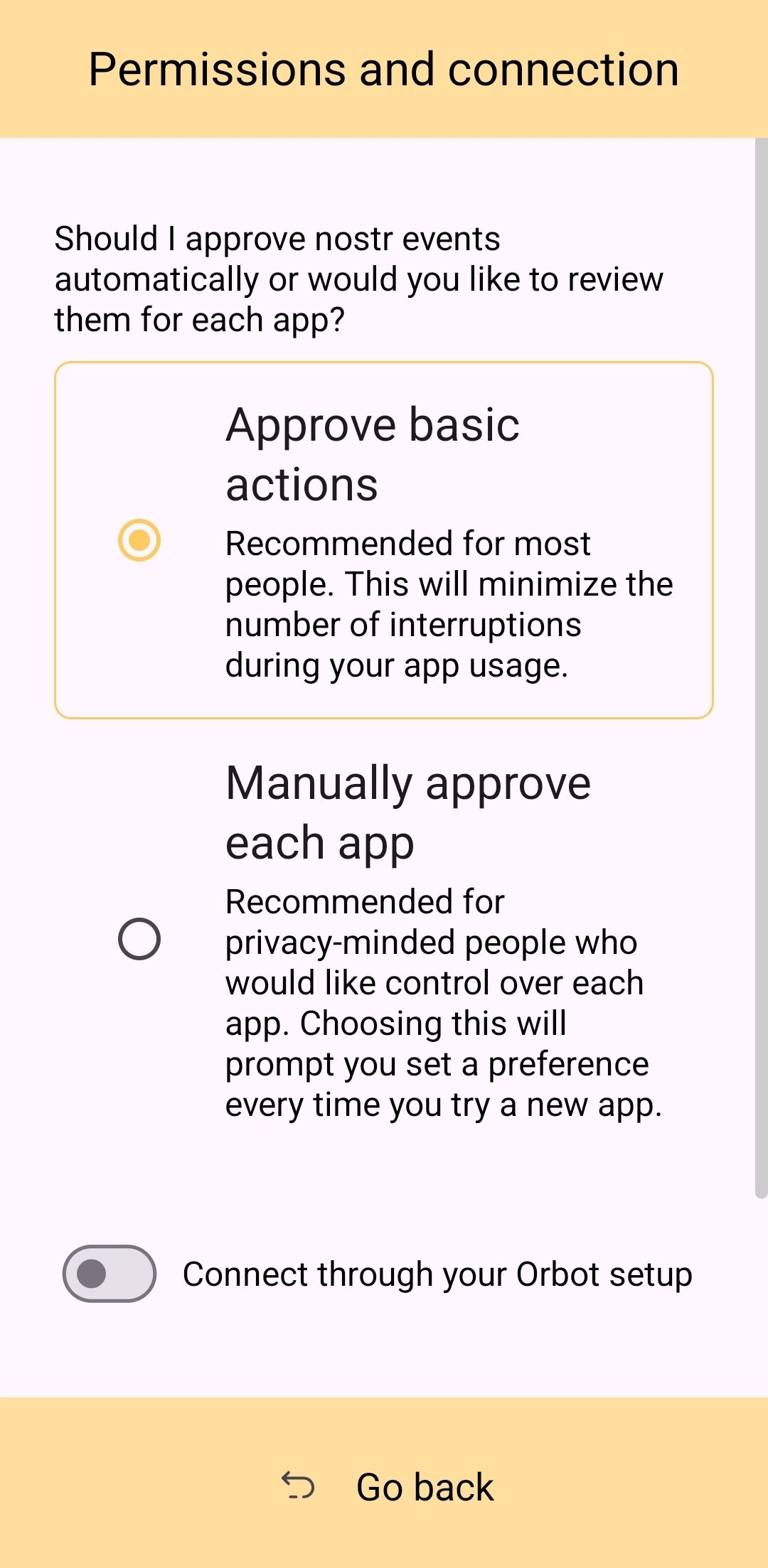
Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with.
This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure.
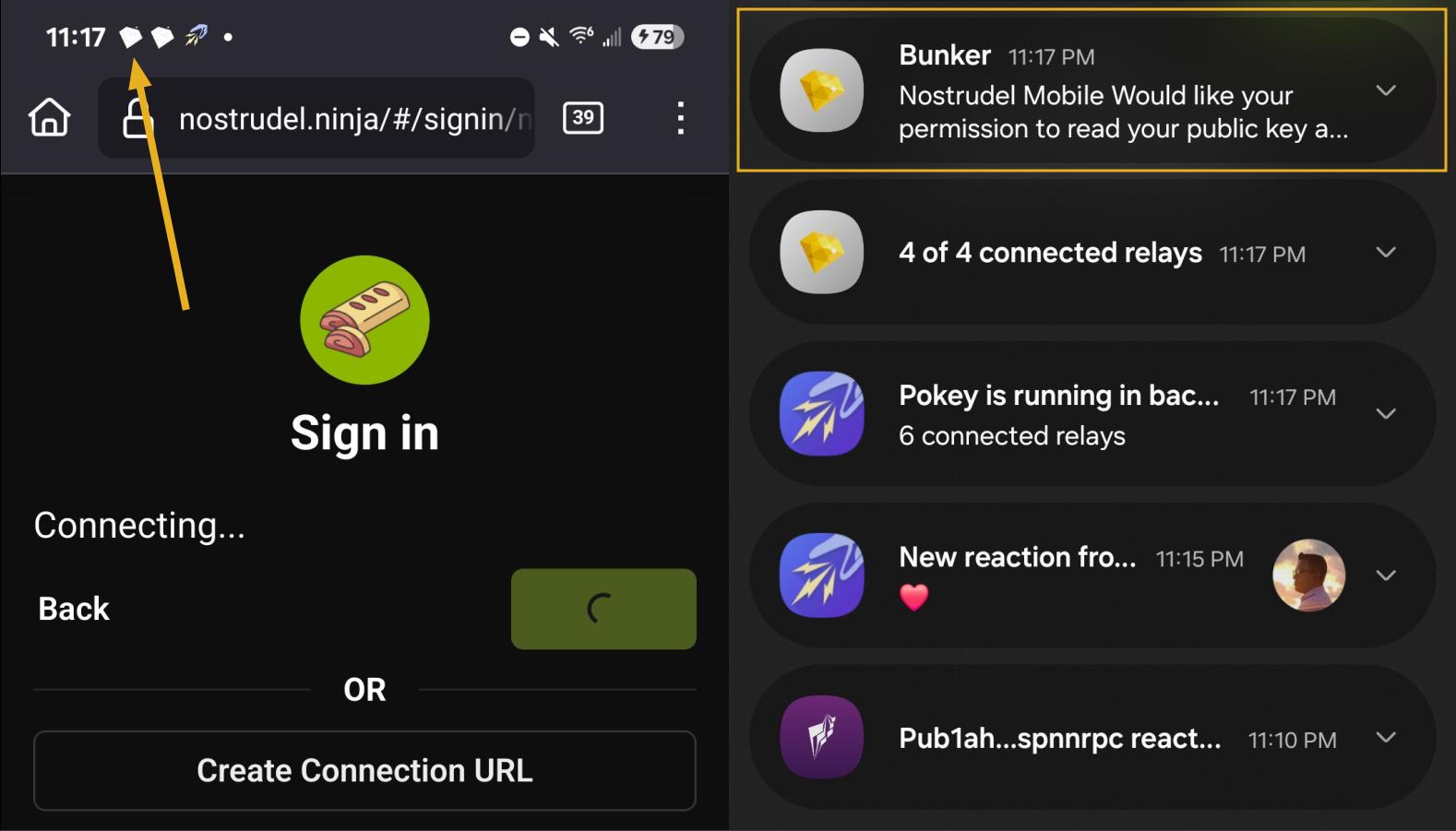
### Nostr Connect/Bunker Signing
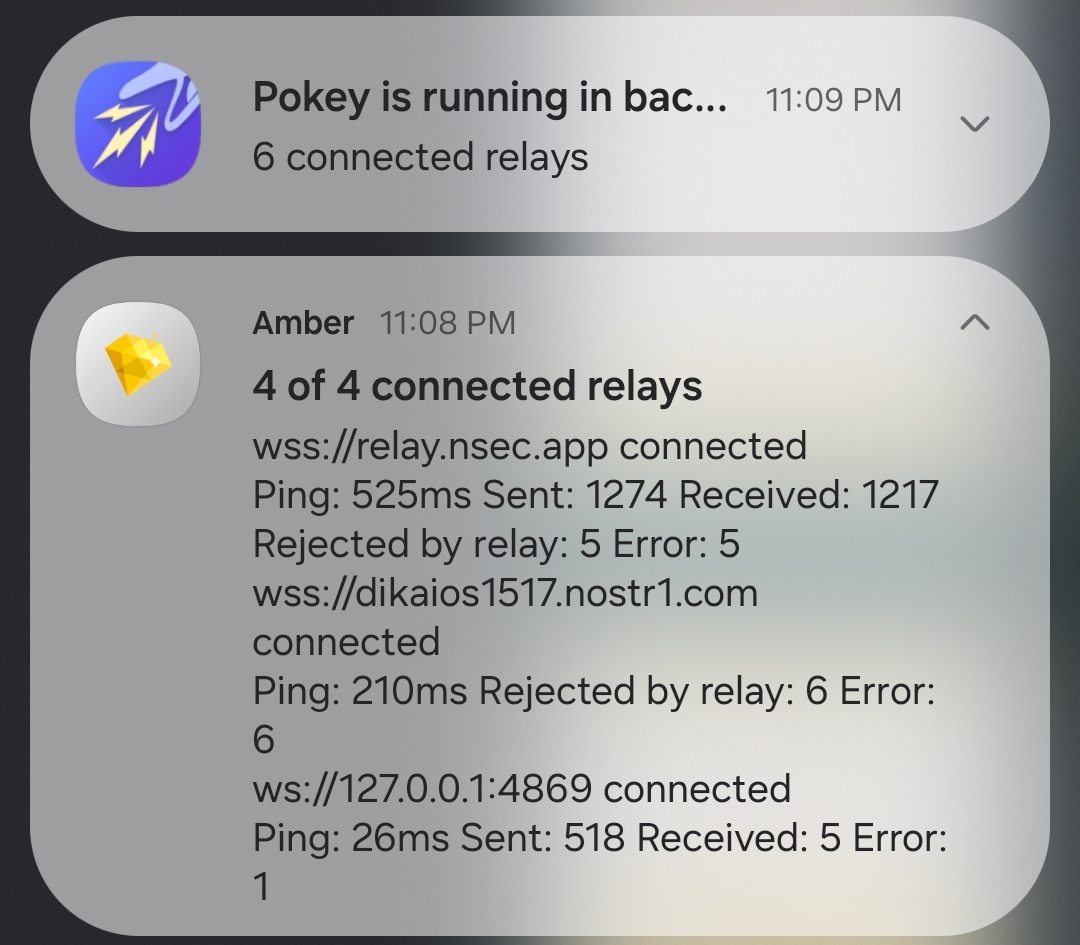
This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable.
Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected.
By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted.
Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc.
The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string.
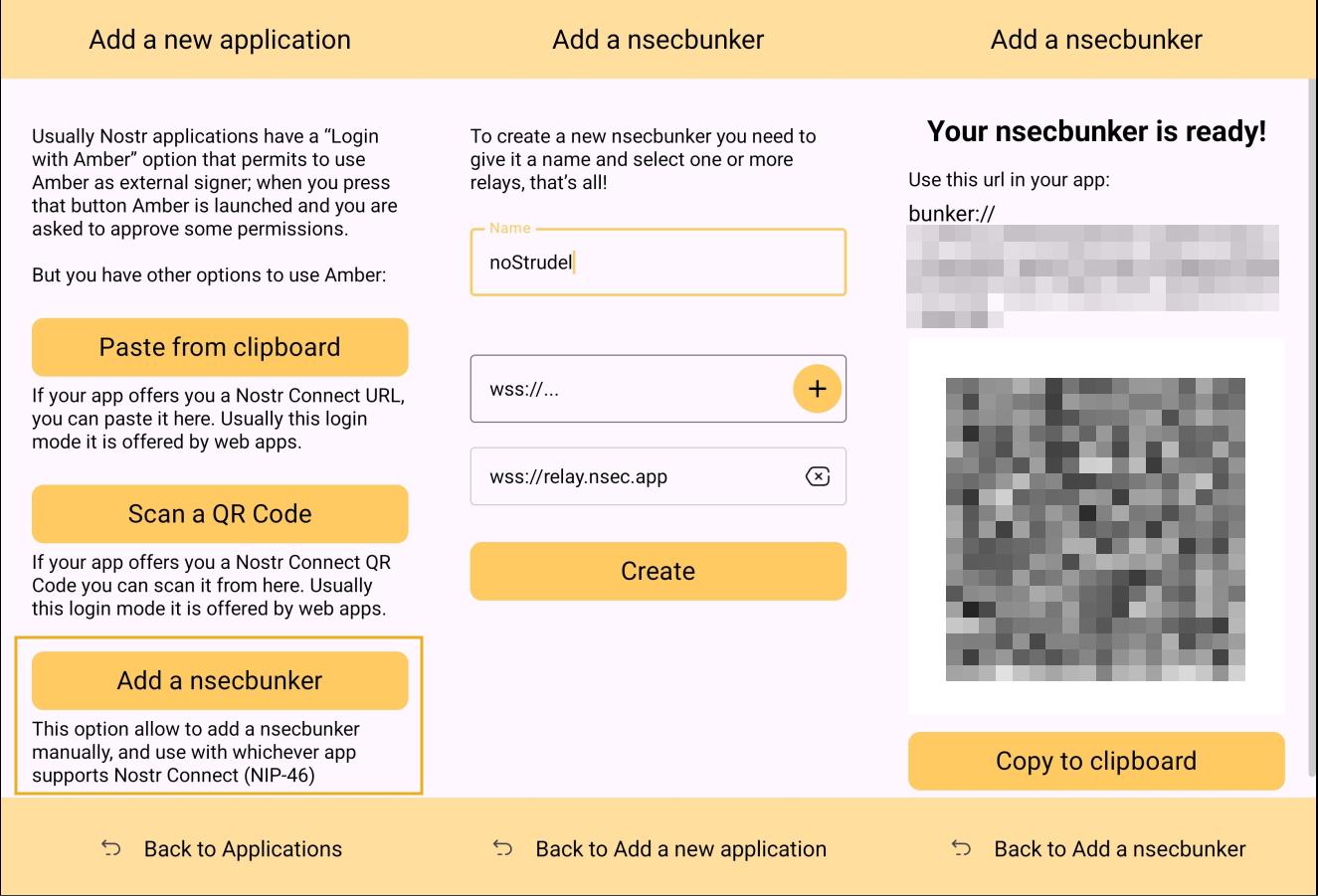
Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone.
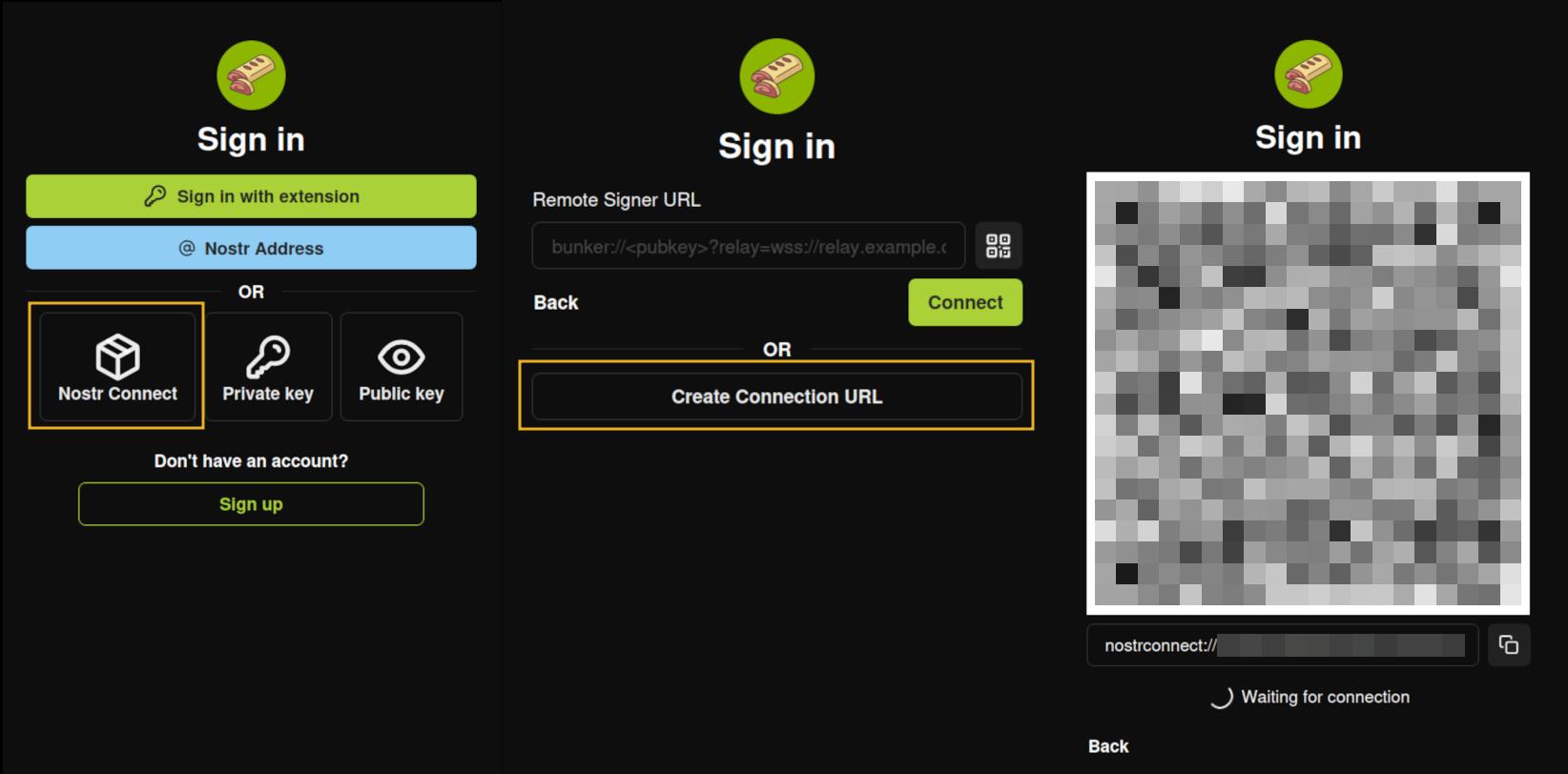
### Multiple Accounts
Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed.
When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for.
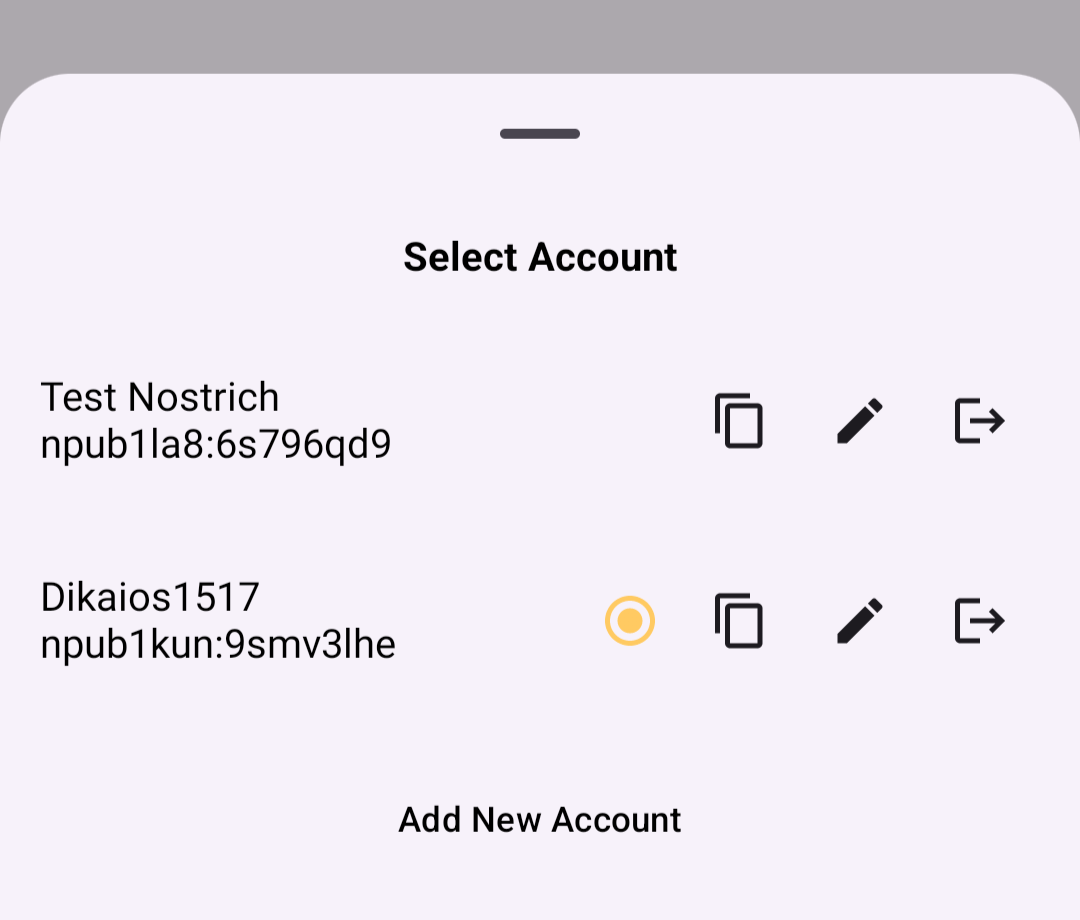
### Key Backup & Restore
Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec.
Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events.
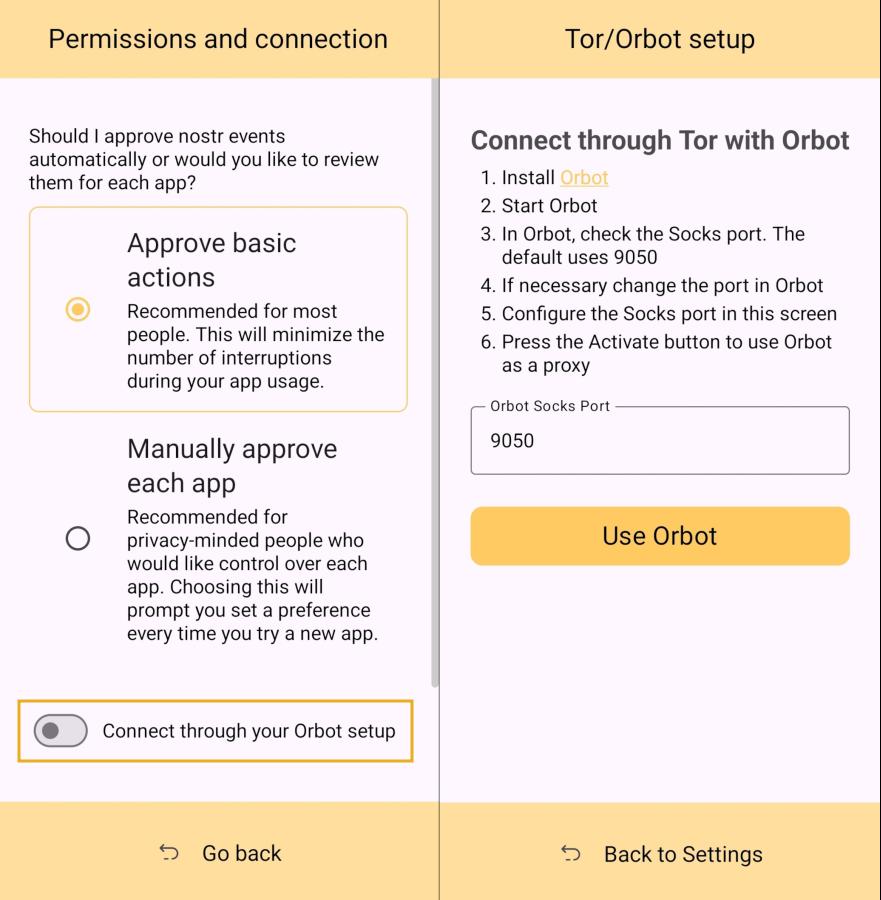
### Tor Support
While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity.
### Additional Security
Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access.
## Can My Grandma Use It?
Score: **4.0** / 5
At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the ***same password*** for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs.
That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touchpoint with Nostr, I think it holds up well, but could be somewhat streamlined.
Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.
The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays.
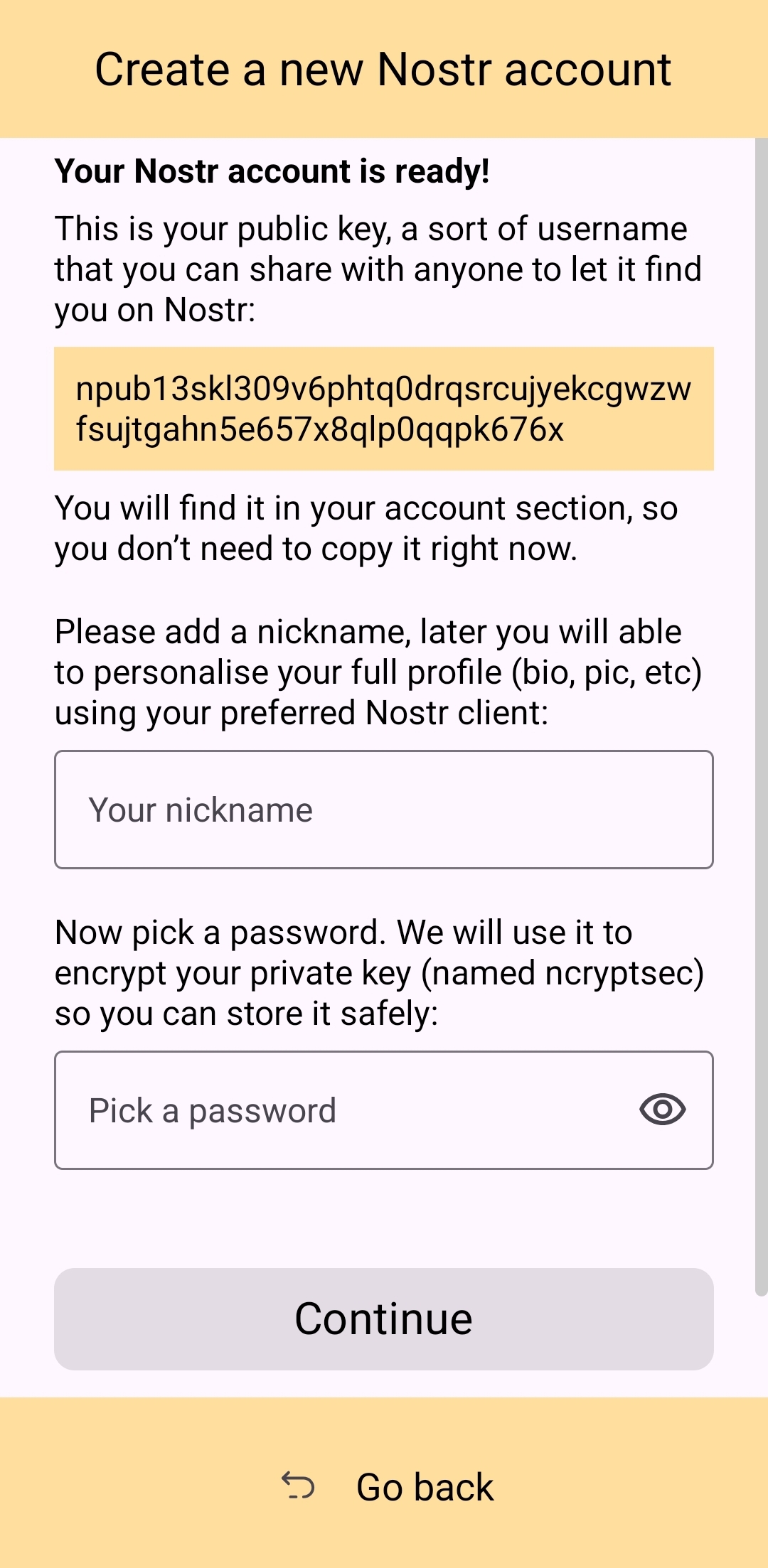
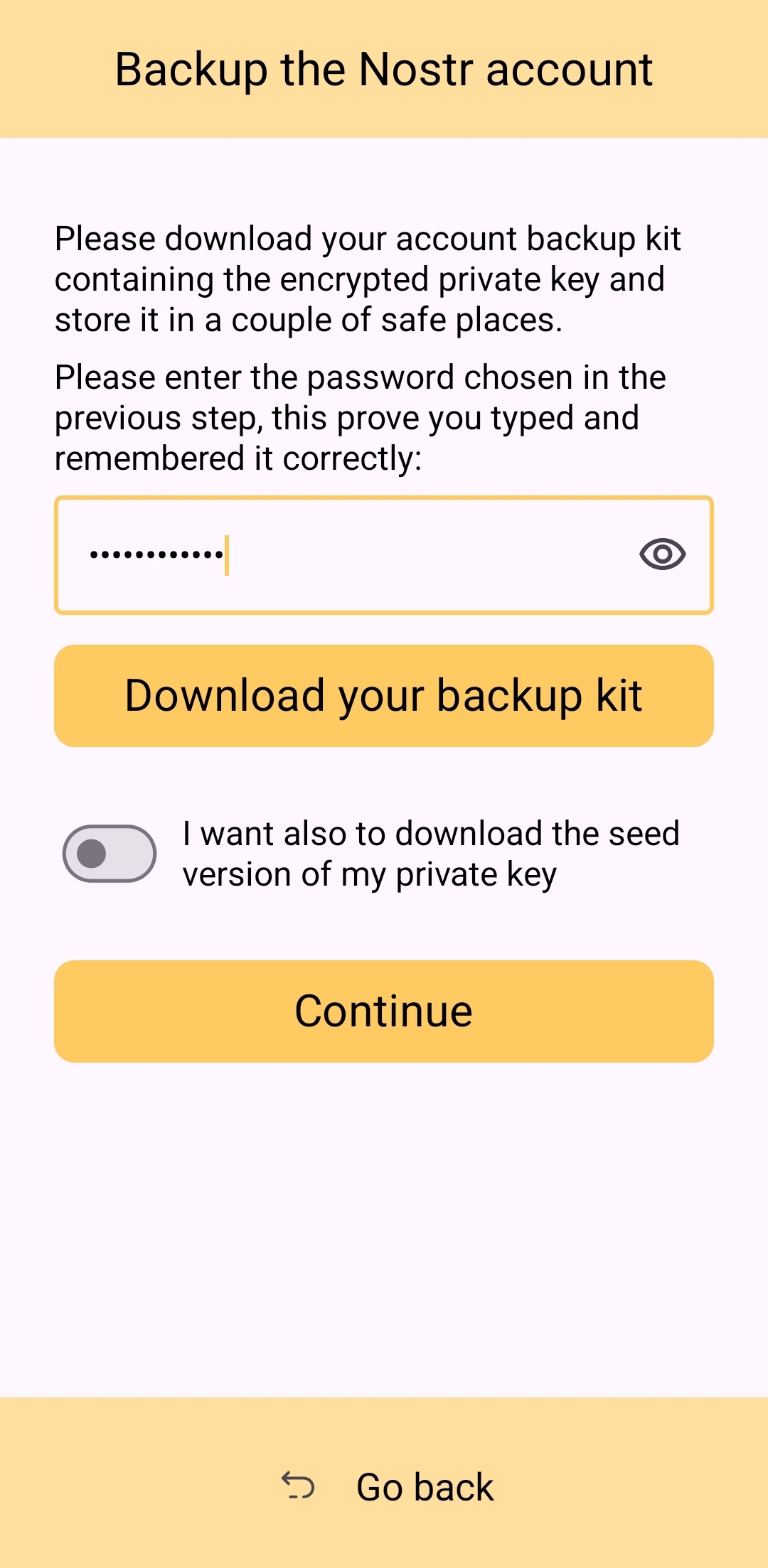
Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action.
Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds.
The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression.
Now, I absolutely ***love*** the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process.
Instead of:
- Install Amber
- Set up your keys
- Install the client you want to use
- Log in with Amber
The process becomes:
- Go to the Zapstore GitHub and download the latest version from the releases page.
- Install the APK you downloaded, allowing any prompt to install unknown apps.
- Open Zapstore and install Amber, allowing any prompt to install unknown apps again.
- Open Amber and set up your keys.
- Install the client you want to use
- Log in with Amber
An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store.
## How do UI Look?
Score: **4.5** / 5
Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case.
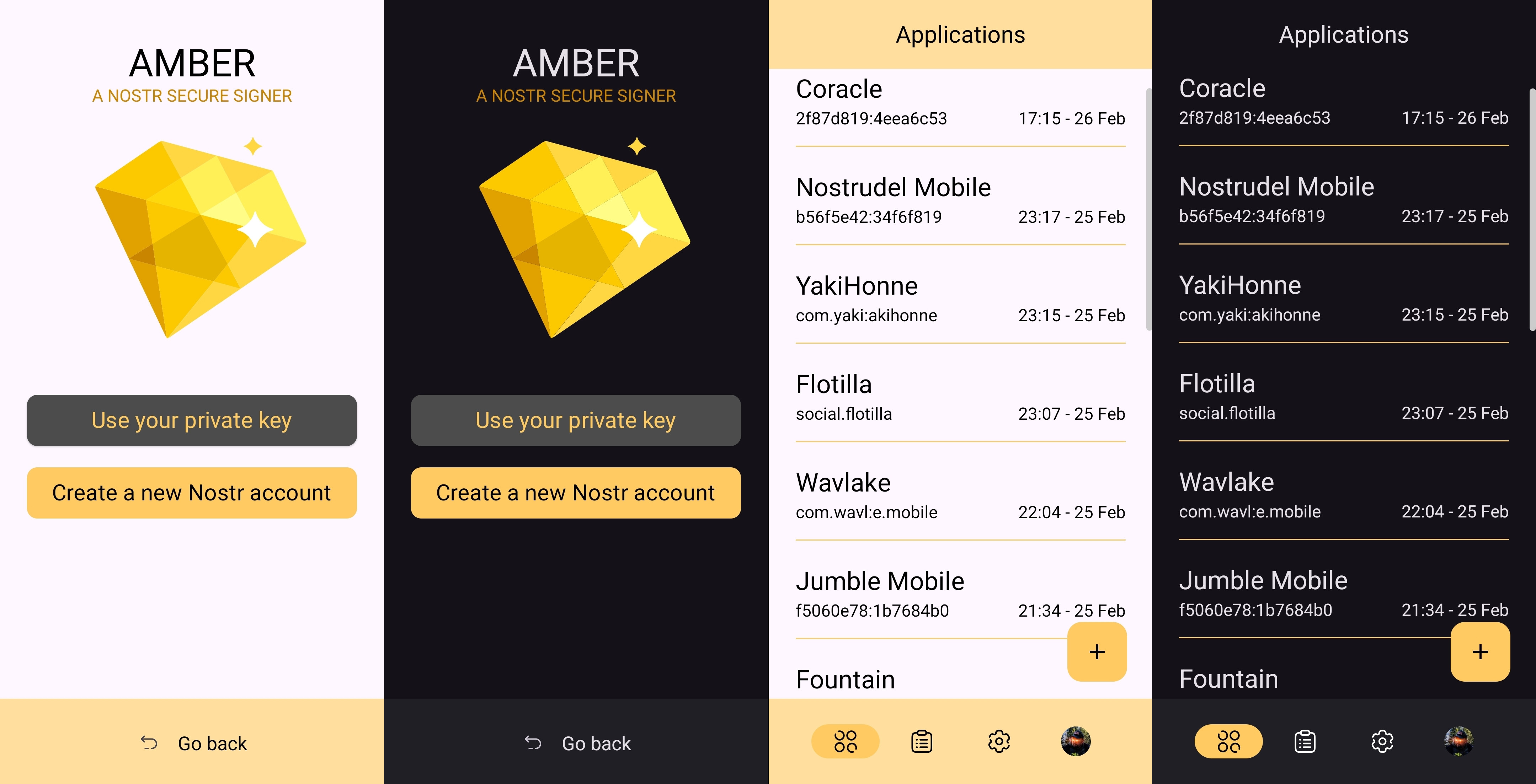
I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name.
It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated.
## Relay Management
Score: **4.9** / 5
Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture.
In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings.
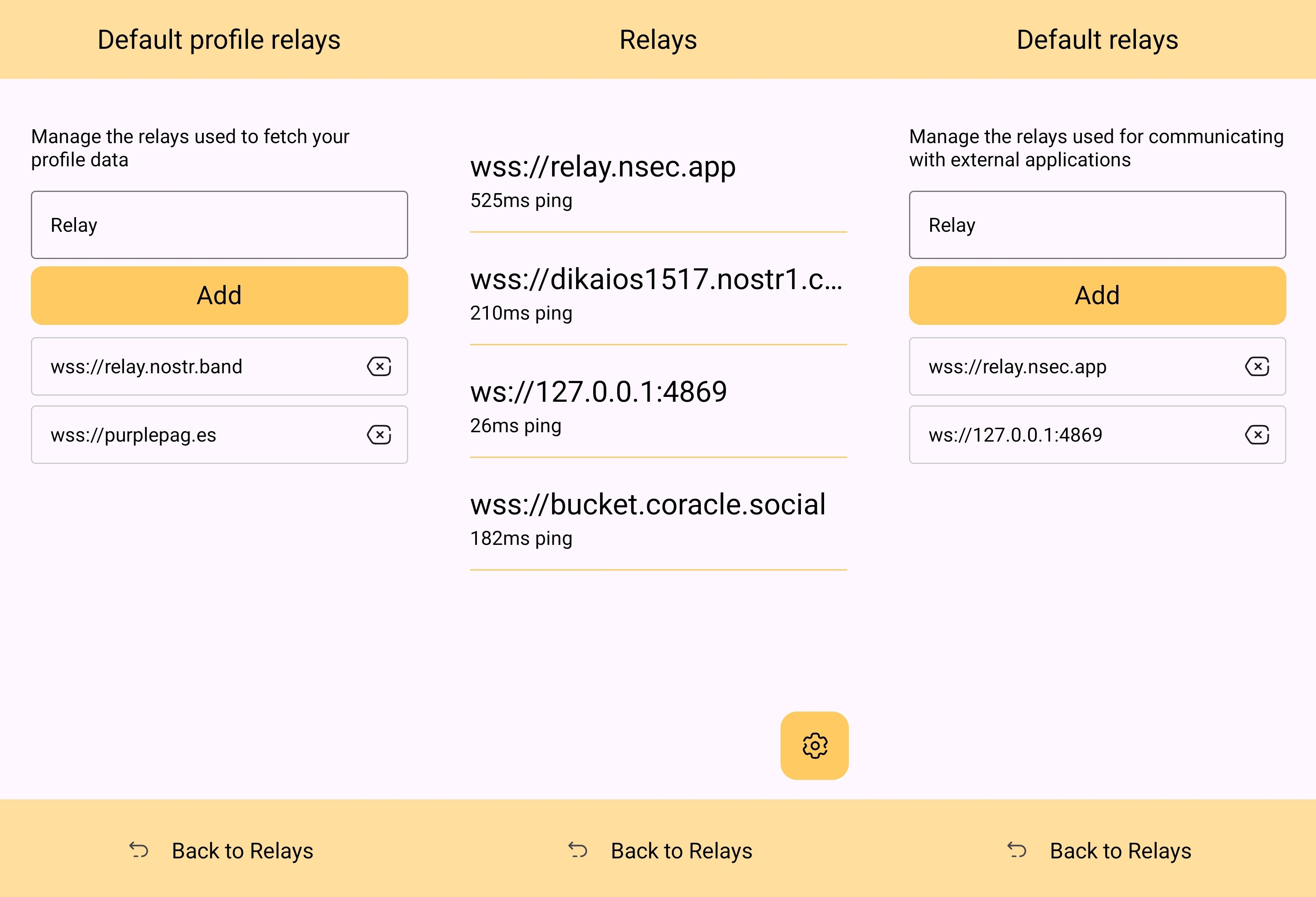
The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps.
Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard.
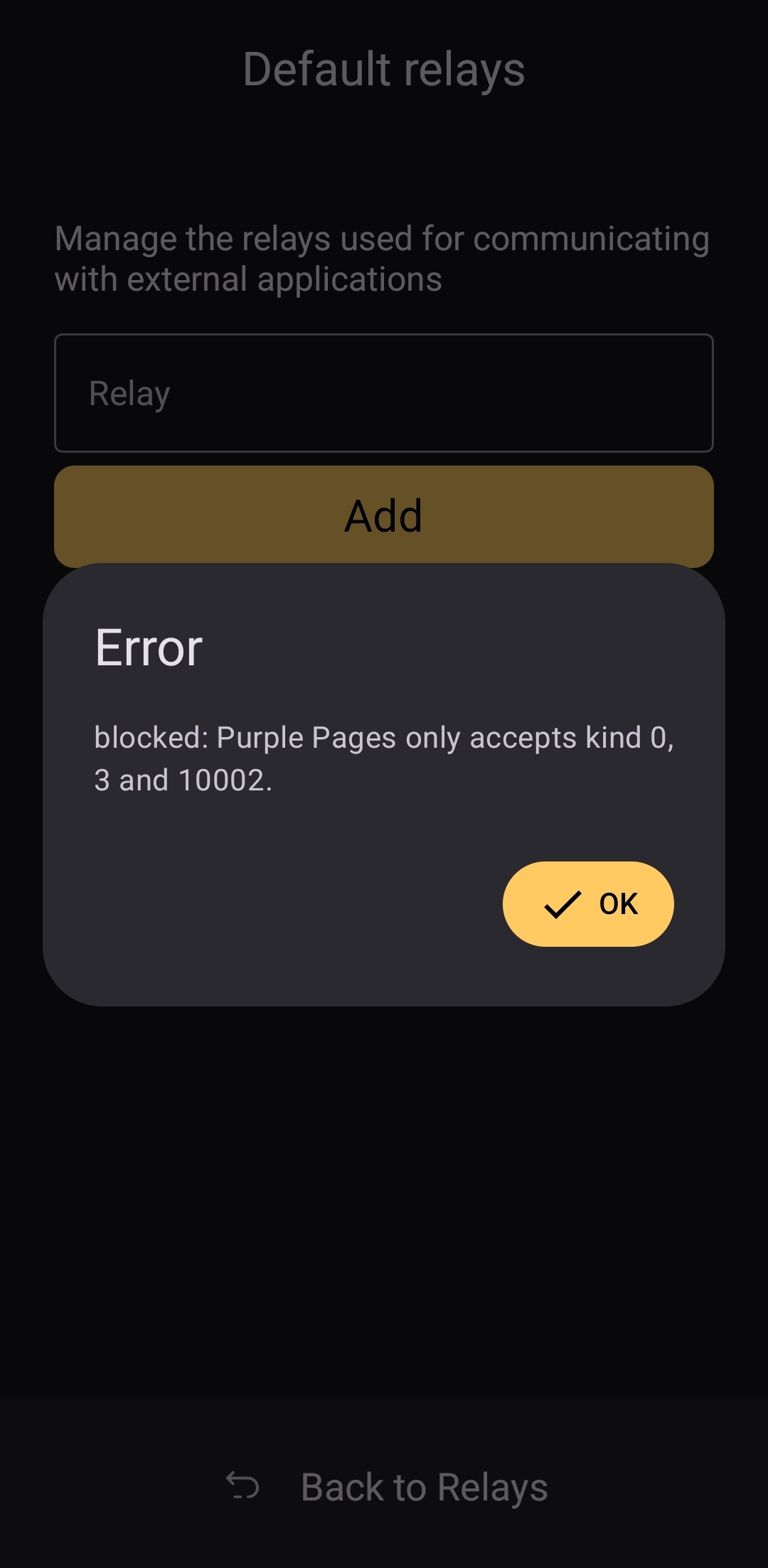
In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber.
The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed.
## Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months.
nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m
This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen.
If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into.
That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about ***how*** to use Amber, and that is a testament to Amber's ease of use all on its own.
## Wrap Up
If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience.
If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing.
Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date!
Now... What should I review next?
-

@ b2d670de:907f9d4a
2025-02-28 16:39:38
# onion-service-nostr-relays
A list of nostr relays exposed as onion services.
## The list
| Relay name | Description | Onion url | Operator | Payment URL | Payment options |
| --- | --- | --- | --- | --- | --- |
| nostr.oxtr.dev | Same relay as clearnet relay nostr.oxtr.dev | ws://oxtrdevav64z64yb7x6rjg4ntzqjhedm5b5zjqulugknhzr46ny2qbad.onion | [operator](nostr:nprofile1qqst94nsmefmya53crp5qq39kewrtgndqcynhnzp7j8lcu0qjple6jspz3mhxue69uhkummnw3ezummcw3ezuer9wcq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7jxrgyy) | N/A | N/A |
| relay.snort.social | Same relay as clearnet relay relay.snort.social | wss://skzzn6cimfdv5e2phjc4yr5v7ikbxtn5f7dkwn5c7v47tduzlbosqmqd.onion | [operator](nostr:nprofile1qqsx8lnrrrw9skpulctgzruxm5y7rzlaw64tcf9qpqww9pt0xvzsfmgpzpmhxue69uhkummnw3ezuamfdejszxrhwden5te0wfjkccte9eekummjwsh8xmmrd9skct9tyup) | N/A | N/A |
| nostr.thesamecat.io | Same relay as clearnet relay nostr.thesamecat.io | ws://2jsnlhfnelig5acq6iacydmzdbdmg7xwunm4xl6qwbvzacw4lwrjmlyd.onion | [operator](nostr:npub1wtuh24gpuxjyvnmjwlvxzg8k0elhasagfmmgz0x8vp4ltcy8ples54e7js) | N/A | N/A |
| nostr.land | The nostr.land paid relay (same as clearnet) | ws://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion | [operator](nostr:npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj) | [Payment URL](http://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion) | BTC LN |
| bitcoiner.social | No auth required, currently | ws://bitcoinr6de5lkvx4tpwdmzrdfdpla5sya2afwpcabjup2xpi5dulbad.onion | [operator](nostr:npub1an3nz7lczcunpdw6ltjst94hgzcxpppnk7zk3zr2nfcj4yd96kdse6twjd) | N/A | N/A |
| relay.westernbtc.com | The westernbtc.com paid relay | ws://westbtcebhgi4ilxxziefho6bqu5lqwa5ncfjefnfebbhx2cwqx5knyd.onion | [operator](nostr:npub1pc57ls4rad5kvsp733suhzl2d4u9y7h4upt952a2pucnalc59teq33dmza) | [Payment URL](hjar34h5zwgtvxr345q7rncso3dhdaryuxgri3lu7lbhmnzvin72z5ad.onion) | BTC LN |
| freelay.sovbit.host | Free relay for sovbit.host | ws://sovbitm2enxfr5ot6qscwy5ermdffbqscy66wirkbsigvcshumyzbbqd.onion | [operator](nostr:npub1gnwpctdec0aa00hfy4lvadftu08ccs9677mr73h9ddv2zvw8fu9smmerrq) | N/A | N/A |
| nostr.sovbit.host | Paid relay for sovbit.host | ws://sovbitgz5uqyh7jwcsudq4sspxlj4kbnurvd3xarkkx2use3k6rlibqd.onion | [operator](nostr:npub1gnwpctdec0aa00hfy4lvadftu08ccs9677mr73h9ddv2zvw8fu9smmerrq) | N/A | N/A |
| nostr.wine | 🍷 [nostr.wine](https://nostr.wine) relay | ws://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion) | BTC LN, BTC, Credit Card/CashApp (Stripe) |
| inbox.nostr.wine | 🍷 [inbox.nostr.wine](https://inbox.nostr.wine) relay | ws://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion) | BTC LN, BTC |
| filter.nostr.wine | 🍷 [filter.nostr.wine](https://filter.nostr.wine) proxy relay | ws://winefiltermhqixxzmnzxhrmaufpnfq3rmjcl6ei45iy4aidrngpsyid.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion/add-time) | BTC LN, BTC |
| N/A | N/A | ws://pzfw4uteha62iwkzm3lycabk4pbtcr67cg5ymp5i3xwrpt3t24m6tzad.onion:81 | [operator](nostr:nprofile1q9z8wue69uhky6t5vdhkjmnjxejx2dtvddm8sdr5wpmkgmt6wfjxversd3sn2umevyexzenhwp3kzcn2w4cry7rsdy6kgatvvfskgtn0de5k7m30q9z8wue69uhk77r5wfjx2anpwcmrg73kx3ukydmcxeex5ee5de685ut2dpjkgmf4vg6h56n3w4k82emtde585u35xeh8jvn3vfskgtn0de5k7m30qqs93v545xjl0w8865rhw7kte0mkjxst88rk3k3xj53q4zdxm2zu5ectdn2z6) | N/A | N/A |
| nostr.fractalized.net | Free relay for fractalized.net | ws://xvgox2zzo7cfxcjrd2llrkthvjs5t7efoalu34s6lmkqhvzvrms6ipyd.onion | [operator](nostr:npub1ky4kxtyg0uxgw8g5p5mmedh8c8s6sqny6zmaaqj44gv4rk0plaus3m4fd2) | N/A | N/A |
| nfrelay.app | [nfrelay.app](https://nfrelay.app) aggregator relay (nostr-filter-relay) | ws://nfrelay6saohkmipikquvrn6d64dzxivhmcdcj4d5i7wxis47xwsriyd.onion | [operator](nostr:npub19dn7fq9hlxwjsdtgf28hyakcdmd73cccaf2u7a7vl42echey7ezs2hwja7) | N/A | N/A
| relay.nostr.net | Public relay from nostr.net (Same as clearnet) | ws://nostrnetl6yd5whkldj3vqsxyyaq3tkuspy23a3qgx7cdepb4564qgqd.onion | [operator](https://nostr.at/aljaz@nostr.si) | N/A | N/A |
| nerostrator | Free to read, pay XMR to relay | ws://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion | [operator](nostr:npub19j7zhftjfjnep4xa7zxhevschkqdvem9zr26dq4myhu6d62p3gqs3htnca) |[Payment URL](http://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion) | XMR |
| nostr.girino.org | Public relay from nostr.girino.org | ws://gnostr2jnapk72mnagq3cuykfon73temzp77hcbncn4silgt77boruid.onion | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A |
| wot.girino.org | WoT relay from wot.girino.org | ws://girwot2koy3kvj6fk7oseoqazp5vwbeawocb3m27jcqtah65f2fkl3yd.onion | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A |
| haven.girino.org/{outbox, inbox, chat, private} | Haven smart relay from haven.girino.org | ws://ghaven2hi3qn2riitw7ymaztdpztrvmm337e2pgkacfh3rnscaoxjoad.onion/{outbox, inbox, chat, private} | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A |
| relay.nostpy.lol | Free Web of Trust relay (Same as clearnet) | ws://pemgkkqjqjde7y2emc2hpxocexugbixp42o4zymznil6zfegx5nfp4id.onion | [operator](nostr:nprofile1qy08wumn8ghj7mn0wd68yttsw43zuam9d3kx7unyv4ezumn9wshszxrhwden5te0dehhxarj9enx6apwwa5h5tnzd9az7qpqg5pm4gf8hh7skp2rsnw9h2pvkr32sdnuhkcx9yte7qxmrg6v4txqr5amve) |N/A | N/A |
| Poster.place Nostr Relay | N/A | ws://dmw5wbawyovz7fcahvguwkw4sknsqsalffwctioeoqkvvy7ygjbcuoad.onion | [operator](nostr:nprofile1qqsr836yylem9deatcu08ekfj8qj9f2aypq8ydt0w8dyng8zp8akjsqpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0ds6xxx6y) | N/A | N/A |
| Azzamo Relay | [Azzamo](https://azzamo.net/relays/) Premium Nostr relay. (paid) | ws://q6a7m5qkyonzb5fk5yv4jyu3ar44hqedn7wjopg737lit2ckkhx2nyid.onion | [operator](nostr:npub1jjn20zj6awa6gz73423zxjqszvkzmqqyhwghwctvgy7ncrwlxg8qdavknm) | [Payment URL](https://azzamo.net/pay) | BTC LN |
| Azzamo Inbox Relay | [Azzamo](https://azzamo.net/inbox-relay/) Group and Private message relay. (Freemium) | ws://gp5kiwqfw7t2fwb3rfts2aekoph4x7pj5pv65re2y6hzaujsxewanbqd.onion | [operator](nostr:npub1jjn20zj6awa6gz73423zxjqszvkzmqqyhwghwctvgy7ncrwlxg8qdavknm) | [Payment URL](https://azzamo.net/pay) | BTC LN |
| Noderunners Relay | The official [Noderunners](https://noderunners.network) Nostr Relay. | ws://35vr3xigzjv2xyzfyif6o2gksmkioppy4rmwag7d4bqmwuccs2u4jaid.onion | [operator](nostr:nprofile1qqsqarzpaw2xv4cc36n092krdsj78yll7n2pfx5rv7fzp4n9jhlsl2spz3mhxue69uhhwmm59esh57npd4hjumn9wsq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tqd6ns) | [Payment URL](https://noderunners.azzamo.net) | BTC LN |
## Contributing
Contributions are encouraged to keep this document alive. Just open a PR and I'll have it tested and merged. The onion URL is the only mandatory column, the rest is just nice-to-have metadata about the relay. Put `N/A` in empty columns.
If you want to contribute anonymously, please contact me on [SimpleX](https://simplex.chat/contact#/?v=2&smp=smp%3A%2F%2F0YuTwO05YJWS8rkjn9eLJDjQhFKvIYd8d4xG8X1blIU%3D%40smp8.simplex.im%2FZ_4q0Nv91wCk8Uekyiaas7NSr-nEDir7%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAvdSLn5QEwrfKQswQGTzlwtXeLMXbzxErv-zOJU6D0y8%253D%26srv%3Dbeccx4yfxxbvyhqypaavemqurytl6hozr47wfc7uuecacjqdvwpw2xid.onion) or send a DM on nostr using a disposable npub.
### Operator column
It is generally preferred to use something that includes a NIP-19 string, either just the string or a url that contains the NIP-19 string in it (e.g. an njump url).
-

@ b2d670de:907f9d4a
2025-02-26 18:27:47
This is a list of nostr clients exposed as onion services. The list is currently actively maintained on [GitHub](https://github.com/0xtrr/onion-service-nostr-clients). Contributions are always appreciated!
| Client name | Onion URL | Source code URL | Admin | Description |
| --- | --- | --- | --- | --- |
| Snort | http://agzj5a4be3kgp6yurijk4q7pm2yh4a5nphdg4zozk365yirf7ahuctyd.onion | https://git.v0l.io/Kieran/snort | [operator](nostr:nprofile1qyvhwumn8ghj7un9d3shjtnndehhyapwwdhkx6tpdshszxnhwden5te0wpuhyctdd9jzuenfv96x5ctx9e3k7mf0qqsx8lnrrrw9skpulctgzruxm5y7rzlaw64tcf9qpqww9pt0xvzsfmg9umdvr) | N/A |
| moStard | http://sifbugd5nwdq77plmidkug4y57zuqwqio3zlyreizrhejhp6bohfwkad.onion/ | https://github.com/rafael-xmr/nostrudel/tree/mostard | [operator](nostr:nprofile1qyv8wumn8ghj7un9d3shjtnddaehgctjvshx7un89uq36amnwvaz7tmzdaehgu3wvf5hgcm0d9h8g7r0ddhjucm0d5hsqgy8wvyzw6l9pn5m47n7tcm5un7t7h5ctx3pjx8nfwh06qq8g6max5zadtyx) | minimalist monero friendly nostrudel fork |
| Nostrudel | http://oxtrnmb4wsb77rmk64q3jfr55fo33luwmsyaoovicyhzgrulleiojsad.onion/ | https://github.com/hzrd149/nostrudel | [operator](nostrnpub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0) | Runs latest tagged docker image |
| Nostrudel Next | http://oxtrnnumsflm7hmvb3xqphed2eqpbrt4seflgmdsjnpgc3ejd6iycuyd.onion/ | https://github.com/hzrd149/nostrudel | [operator](nostr:npub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0) | Runs latest "next" tagged docker image |
| Nsite | http://q457mvdt5smqj726m4lsqxxdyx7r3v7gufzt46zbkop6mkghpnr7z3qd.onion/ | https://github.com/hzrd149/nsite-ts | [operator](nostr:nprofile1qqszv6q4uryjzr06xfxxew34wwc5hmjfmfpqn229d72gfegsdn2q3fgpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0dsxx2q3a) | Runs nsite. You can read more about nsite [here](https://github.com/lez/nsite). |
| Shopstr | http://6fkdn756yryd5wurkq7ifnexupnfwj6sotbtby2xhj5baythl4cyf2id.onion/ | https://github.com/shopstr-eng/shopstr-hidden-service | [operator](nostr:nprofile1qqsdxm5qs0a8kdk6aejxew9nlx074g7cnedrjeggws0sq03p4s9khmqpz9mhxue69uhkummnw3ezuamfdejj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhksctkv4hzucmpd3mxztnyv4mz747p6g5) | Runs the latest `serverless` branch build of Shopstr. |
-

@ 4857600b:30b502f4
2025-02-20 19:09:11
Mitch McConnell, a senior Republican senator, announced he will not seek reelection.
At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering.
McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era.
-

@ 94a6a78a:0ddf320e
2025-02-19 21:10:15
Nostr is a revolutionary protocol that enables **decentralized, censorship-resistant communication**. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on **users, developers, and relay operators**.
If you believe in **free speech, decentralization, and an open internet**, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, **every effort helps build a more robust network**.
Here’s how you can get involved and make a difference.
---
## **1️⃣ Use Nostr Daily**
The simplest and most effective way to contribute to Nostr is by **using it regularly**. The more active users, the stronger and more valuable the network becomes.
✅ **Post, comment, and zap** (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\
✅ **Engage with new users** and help them understand how Nostr works.\
✅ **Try different Nostr clients** like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience.
Your activity **keeps the network alive** and helps encourage more developers and relay operators to invest in the ecosystem.
---
## **2️⃣ Run Your Own Nostr Relay**
Relays are the **backbone of Nostr**, responsible for distributing messages across the network. The more **independent relays exist**, the stronger and more censorship-resistant Nostr becomes.
✅ **Set up your own relay** to help decentralize the network further.\
✅ **Experiment with relay configurations** and different performance optimizations.\
✅ **Offer public or private relay services** to users looking for high-quality infrastructure.
If you're not technical, you can still **support relay operators** by **subscribing to a paid relay** or donating to open-source relay projects.
---
## **3️⃣ Support Paid Relays & Infrastructure**
Free relays have helped Nostr grow, but they **struggle with spam, slow speeds, and sustainability issues**. **Paid relays** help fund **better infrastructure, faster message delivery, and a more reliable experience**.
✅ **Subscribe to a paid relay** to help keep it running.\
✅ **Use premium services** like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\
✅ **Donate to relay operators** who invest in long-term infrastructure.
By funding **Nostr’s decentralized backbone**, you help ensure its **longevity and reliability**.
---
## **4️⃣ Zap Developers, Creators & Builders**
Many people contribute to Nostr **without direct financial compensation**—developers who build clients, relay operators, educators, and content creators. **You can support them with zaps!** ⚡
✅ **Find developers working on Nostr projects** and send them a zap.\
✅ **Support content creators and educators** who spread awareness about Nostr.\
✅ **Encourage builders** by donating to open-source projects.
Micro-payments via the **Lightning Network** make it easy to directly **support the people who make Nostr better**.
---
## **5️⃣ Develop New Nostr Apps & Tools**
If you're a developer, you can **build on Nostr’s open protocol** to create new apps, bots, or tools. Nostr is **permissionless**, meaning anyone can develop for it.
✅ **Create new Nostr clients** with unique features and user experiences.\
✅ **Build bots or automation tools** that improve engagement and usability.\
✅ **Experiment with decentralized identity, authentication, and encryption** to make Nostr even stronger.
With **no corporate gatekeepers**, your projects can help shape the future of decentralized social media.
---
## **6️⃣ Promote & Educate Others About Nostr**
Adoption grows when **more people understand and use Nostr**. You can help by **spreading awareness** and creating educational content.
✅ **Write blogs, guides, and tutorials** explaining how to use Nostr.\
✅ **Make videos or social media posts** introducing new users to the protocol.\
✅ **Host discussions, Twitter Spaces, or workshops** to onboard more people.
The more people **understand and trust Nostr**, the stronger the ecosystem becomes.
---
## **7️⃣ Support Open-Source Nostr Projects**
Many Nostr tools and clients are **built by volunteers**, and open-source projects thrive on **community support**.
✅ **Contribute code** to existing Nostr projects on GitHub.\
✅ **Report bugs and suggest features** to improve Nostr clients.\
✅ **Donate to developers** who keep Nostr free and open for everyone.
If you're not a developer, you can still **help with testing, translations, and documentation** to make projects more accessible.
---
## **🚀 Every Contribution Strengthens Nostr**
Whether you:
✔️ **Post and engage daily**\
✔️ **Zap creators and developers**\
✔️ **Run or support relays**\
✔️ **Build new apps and tools**\
✔️ **Educate and onboard new users**
**Every action helps make Nostr more resilient, decentralized, and unstoppable.**
Nostr isn’t just another social network—it’s **a movement toward a free and open internet**. If you believe in **digital freedom, privacy, and decentralization**, now is the time to get involved.
-

@ 16f1a010:31b1074b
2025-02-19 20:57:59
In the rapidly evolving world of Bitcoin, running a Bitcoin node has become more accessible than ever. Platforms like Umbrel, Start9, myNode, and Citadel offer user-friendly interfaces to simplify node management. However, for those serious about maintaining a robust and efficient Lightning node ⚡, relying solely on these platforms may not be the optimal choice.
Let’s delve into why embracing **Bitcoin Core** and mastering the command-line interface (CLI) can provide a **more reliable, sovereign, and empowering** experience.
### Understanding Node Management Platforms
#### What Are Umbrel, Start9, myNode, and Citadel?
Umbrel, Start9, myNode, and Citadel are platforms designed to streamline the process of running a Bitcoin node. They offer graphical user interfaces (GUIs) that allow users to manage various applications, including Bitcoin Core and Lightning Network nodes, through a web-based dashboard 🖥️.
These platforms often utilize Docker containers 🐳 to encapsulate applications, providing a modular and isolated environment for each service.

#### The Appeal of Simplified Node Management
The primary allure of these platforms lies in their simplicity. With minimal command-line interaction, users can deploy a full Bitcoin and Lightning node, along with a suite of additional applications.
✅ **Easy one-command installation**
✅ **Web-based GUI for management**
✅ **Automatic app updates** *(but with delays, as we’ll discuss)*
However, while this convenience is attractive, it comes **at a cost**.
### The Hidden Complexities of Using Node Management Platforms
While the user-friendly nature of these platforms is advantageous, it can also introduce several challenges that may hinder advanced users or those seeking greater control over their nodes.
#### 🚨 Dependency on Maintainers for Updates
One significant concern is the reliance on platform maintainers for updates. Since these platforms manage applications through Docker containers, users must wait for the maintainers to update the container images before they can access new features or security patches.
🔴 **Delayed Bitcoin Core updates = potential security risks**
🔴 **Lightning Network updates are not immediate**
🔴 **Bugs and vulnerabilities may persist longer**
Instead of waiting on a third party, **why not update Bitcoin Core & LND yourself instantly**?
#### ⚙️ Challenges in Customization and Advanced Operations
For users aiming to perform advanced operations, such as:
* Custom backups 📂
* Running specific CLI commands 🖥️
* Optimizing node settings ⚡
…the **abstraction layers introduced by these platforms become obstacles**.
Navigating through nested directories and issuing commands inside Docker containers **makes troubleshooting a nightmare**. Instead of a simple `bitcoin-cli` command, you must figure out how to execute it inside the container, adding unnecessary complexity.
#### Increased Backend Complexity
To achieve **frontend simplicity**, these platforms make the backend more complex.
🚫 Extra layers of abstraction
🚫 Hidden logs and settings
🚫 Harder troubleshooting
The use of **multiple Docker containers**, **custom scripts**, and **unique file structures** can **make system maintenance and debugging a pain**.
This **complication defeats the purpose** of “making running a node easy.”
## ✅ Advantages of Using Bitcoin Core and Command-Line Interface (CLI)
By installing Bitcoin Core directly and using the command-line interface (CLI), you gain several key advantages that make managing a Bitcoin and Lightning node more efficient and empowering.
#### Direct Control and Immediate Updates
One of the biggest downsides of package manager-based platforms is the reliance on third-party maintainers to release updates. Since Bitcoin Core, Lightning implementations (such as LND, Core Lightning, or Eclair), and other related software evolve rapidly, waiting for platform-specific updates can leave you running outdated or vulnerable versions.
By installing Bitcoin Core directly, you remove this dependency. You can update immediately when new versions are released, ensuring your node benefits from the latest features, security patches, and bug fixes. The same applies to Lightning software—being able to install and update it yourself gives you full autonomy over your node’s performance and security.
#### 🛠 Simplified System Architecture
Platforms like Umbrel and myNode introduce extra complexity by running Bitcoin Core and Lightning inside Docker containers. This means:
* The actual files and configurations are stored inside Docker’s filesystem, making it **harder to locate and manage them manually**.
* If something breaks, **troubleshooting is more difficult** due to the added layer of abstraction.
* Running commands requires jumping through Docker shell sessions, adding unnecessary friction to what should be a straightforward process.
Instead, a direct installation of Bitcoin Core, Lightning, and Electrum Server (if needed) results in a **cleaner, more understandable system**. The software runs natively on your machine, without containerized layers making things more convoluted.
Additionally, setting up your own systemd service files for Bitcoin and Lightning** is not as complicated as it seems**. Once configured, these services will run automatically on boot, offering the same level of convenience as platforms like Umbrel but without the unnecessary complexity.
#### Better Lightning Node Management
If you’re running a **Lightning Network node**, using CLI-based tools provides far more flexibility than relying on a GUI like the ones bundled with node management platforms.
🟢 **Custom Backup Strategies** – Running Lightning through a GUI-based node manager often means backups are handled in a way that is opaque to the user. With CLI tools, you can easily script automatic backups of your channels, wallets, and configurations.
🟢 **Advanced Configuration** – Platforms like Umbrel force certain configurations by default, limiting how you can customize your Lightning node. With a direct install, you have full control over:
* Channel fees 💰
* Routing policies 📡
* Liquidity management 🔄
🟢 **Direct Access to LND, Core Lightning, or Eclair** – Instead of issuing commands through a GUI (which is often limited in functionality), you can use:
* `lncli` (for LND)
* `lightning-cli` (for Core Lightning)
…to interact with your node at a deeper level.
#### Enhanced Learning and Engagement
A crucial aspect of running a Bitcoin and Lightning node is **understanding how it works**.
Using an abstraction layer like Umbrel may get a node running in a few clicks, but **it does little to teach users how Bitcoin actually functions**.
By setting up Bitcoin Core, Lightning, and related software manually, you will:
✅ Gain practical knowledge of Bitcoin nodes, networking, and system performance.
✅ Learn how to configure and manage RPC commands.
✅ Become less reliant on third-party developers and more confident in troubleshooting.
🎯 **Running a Bitcoin node is about sovereignty – learn how to control it yourself**.
## Become more sovereign TODAY
Many guides make this process **straightforward**
[K3tan](https://k3tan.com/about) has a fantastic guide on running Bitcoin Core, Electrs, LND and more.
- [Ministry of Nodes Guide 2024](https://www.youtube.com/playlist?list=PLCRbH-IWlcW0g0HCrtI06_ZdVVolUWr39)
- You can find him on nostr
nostr:npub1txwy7guqkrq6ngvtwft7zp70nekcknudagrvrryy2wxnz8ljk2xqz0yt4x
Even with the best of guides, if you are running this software,
📖 **READ THE DOCUMENTATION**
This is all just software at the end of the day. Most of it is very well documented. Take a moment to actually read through the documentation for yourself when installing. The documentation has step by step guides on setting up the software.
Here is a helpful list:
* [Bitcoin.org Bitcoin Core Linux install instructions](https://bitcoin.org/en/full-node#linux-instructions)
* [Bitcoin Core Code Repository](https://github.com/bitcoin/bitcoin)
* [Electrs Installation](https://github.com/romanz/electrs/blob/master/doc/install.md)
* [LND Documentation](https://docs.lightning.engineering/)
* [LND Code Repository](https://github.com/lightningnetwork/lnd)
* [CLN Documentation](https://docs.corelightning.org/docs/home)
* [CLN Code Repository](https://github.com/ElementsProject/lightning)
*If you have any more resources or links I should add, please comment them . I want to add as much to this article as I can.*
-

@ 266815e0:6cd408a5
2025-02-18 17:25:31
## noStrudel
Released another major version of noStrudel v0.42.0
Which included a few new features and a lot of cleanup
nostr:naddr1qvzqqqr4gupzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqp3hx7um5wf6kgetv956ry6rmhwr
## Blossom
On the blossom front there where a few more PRs
- Expanded the documentation around CORS headers in BUD-01 thanks to nostr:npub1a6we08n7zsv2na689whc9hykpq4q6sj3kaauk9c2dm8vj0adlajq7w0tyc
- Made auth optional on the `/upload` endpoint [PR](https://github.com/hzrd149/blossom/pull/33)
- Added a `HEAD /media` endpoint for BUD-05 [PR](https://github.com/hzrd149/blossom/pull/42)
- Added range request recommendations to BUD-01 [PR](https://github.com/hzrd149/blossom/pull/47)
With blossom uploads starting to be supported in more nostr clients users where starting to ask where to find a list of blossom servers. so I created a simple nostr client that allows users to post servers and leave reviews
[blossomservers.com](https://blossomservers.com)
Its still very much a work in progress (needs login and server and review editing)
The source is on [github](https://github.com/hzrd149/blossomservers)
I also started another project to create a simple account based paid blossom server [blossom-account-server](https://github.com/hzrd149/blossom-account-server)
Unfortunately I got sidetracked and I didn't have the time to give it the attention it needs to get it over the finish line
## Smaller projects
- [cherry-tree](https://github.com/hzrd149/cherry-tree) A small app for uploading chunked blobs to blossom servers (with cashu payment support)
- [vite-plugin-funding](https://github.com/hzrd149/vite-plugin-funding) A vite plugin to collect and expose package "funding" to the app
- [node-red-contrib-rx-nostr](https://github.com/hzrd149/node-red-contrib-rx-nostr) The start of a node-red package for rx-nostr. if your interested please help
- [node-red-contrib-applesauce](https://github.com/hzrd149/node-red-contrib-applesauce) The start of a node-red package for applesauce. I probably wont finish it so any help it welcome
## Plans for 2025
I have a few vague ideas of what I want to work on Q1 of 2025. but there are a few things i know for certain.
I'm going to keep refactoring noStrudel by moving core logic out into [applesauce](https://hzrd149.github.io/applesauce/) and making it more modular. This should make noStrudel more reliable and hopefully allow me to create and maintain more apps with less code
And I'm going to write tests. tests for everything. hopefully tests for all the libraries and apps I've created in 2024.
A lot of the code I wrote in 2024 was hacky code to see if things could work. and while its been working pretty well I'm starting to forget the details of of the code I wrote so I cant be sure if it still works or how well it works.
So my solution is to write tests, lots of tests :)
-

@ fd208ee8:0fd927c1
2025-02-15 07:37:01
E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is
* a **transaction on a relay** that triggers
* a **transaction on a mint** that triggers
* a **transaction on Lightning** that triggers
* a **transaction on Bitcoin**.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md
https://github.com/nostr-protocol/nips/blob/master/61.md
-

@ 19220736:7578e0e9
2025-02-14 03:44:21
While Zelle promotes itself as a quick and easy way to send money, its instant, irreversible transactions have made it a prime target for fraudsters. Despite mounting reports of consumer losses, banks continue to deny reimbursement for many fraud victims, citing narrow legal loopholes. Meanwhile, Early Warning Services, the company behind Zelle, profits from the vast consumer data it collects, fueling concerns about privacy and corporate exploitation. With government investigations ramping up and public pressure mounting, Zelle and their bank owners have teamed up with the Aspen Institute, forming a new task force with corporate and government players.
In 2017, [Early Warning Services](https://www.earlywarning.com/about), owned by Bank of America, Capital One, JPMorgan Chase, PNC Bank, Trust, U.S. Bank, and Wells Fargo, released the [Zelle](https://www.zellepay.com/faq/what-zelle) payment system. It was a fast way to send and receive funds peer to peer between different bank accounts by only needing either the other person's email address or their U.S. mobile phone number.
By 2018, there were growing [concerns](https://www.nytimes.com/2018/04/22/business/zelle-banks-fraud.html) about fraud on Zelle. Despite its convenience, Zelle's design allows funds to transfer instantly and irreversibly, making it a target for scammers. Victims reported being defrauded through tactics like fake online sales or impersonation schemes, and many struggled to recover lost funds due to inconsistent fraud policies among banks. Consumer advocates criticized the platform for inadequate protections, urging banks to implement stronger safeguards to prevent fraud and better support affected customers.
In 2022, a Senate report [criticized](https://www.bankingdive.com/news/warren-zelle-fraud-scams-report-truist-pnc-us-bank-america-jpmorgan-wells-fargo-aba-bpi-cba/633305/) major U.S. banks, including JPMorgan Chase, Bank of America, and Wells Fargo, for failing to adequately protect consumers from fraud on the Zelle payment platform. The investigation revealed that these banks often deny reimbursement for scams where victims are tricked into transferring funds, citing a narrow interpretation of liability under the Electronic Fund Transfer Act. (*"While banks bear responsibility for unauthorized transactions to scammers, consumer-authorized transactions made to fraudsters are another matter”*.) Jamie Dimon, CEO of JPMorgan Chase, [explained](https://www.bankingdive.com/news/bank-ceos-defend-zelle-in-senate-hearing/632554/), *“Anything unauthorized, we do cover”*
On June 16, 2023, the United States Senate Committee on Homeland Security and Governmental Affairs subcommittee, the Permanent Subcommittee on Investigations, launched an inquiry into Early Warning Services and the three largest banks that co-own EWS: JPMorgan Chase, Bank of America, and Wells Fargo.
After a 15-month investigation, the Senate Permanent Subcommittee on Investigations released a [report](https://www.hsgac.senate.gov/wp-content/uploads/2024.7.23-PSI-Majority-Staff-Report-on-Zelle.pdf) on July 23, 2024, highlighting consumer fraud issues tied to the Zelle payment network. The report noted significant drops in the percentage of fraud disputes reimbursed—from 62% in 2019 to just 38% in 2023. Between 2021 and 2023 Zelle [refused](https://dailyhodl.com/2024/07/25/jpmorgan-chase-wells-fargo-and-bank-of-america-refuse-to-reimburse-863000000-to-customers-in-repeated-relentless-failure-to-protect-victims-of-fraud-us-senate-investigation/) to reimburse $880 million to customers who fell victim to fraud on their payment network. Bank employees were found to have broad discretion in deciding whether to reimburse fraud claims, often denying compensation without clear justification. This has raised questions about whether banks are meeting legal obligations under the Electronic Fund Transfer Act ([Regulation E](https://www.consumerfinance.gov/rules-policy/regulations/1005/))
Early Warning Services (EWS) runs the payment network Zelle at a financial loss but generates revenue by selling data-based services to financial institutions. EWS collects extensive consumer and bank data through its operation of Zelle and daily data-sharing agreements with its member banks. This data is used to develop fraud and risk management products, which EWS sells to financial institutions as its primary profit source. While EWS asserts it has not commercialized this data beyond these financial products, the sale of such services remains its main revenue driver.
On August 4, 2024, Senator Richard Blumenthal sent a [letter](https://www.hsgac.senate.gov/wp-content/uploads/2024.08.04-Blumenthal-Letter-to-Chopra.pdf) to CFPB Director Rohit Chopra urging immediate action to address fraud concerns tied to the Zelle payment platform. The letter calls for the Consumer Financial Protection Bureau (CFPB) to investigate their dispute resolution practices and ensure that they fully and promptly address consumer fraud reports. On August 7, 2024, it was [reported](https://www.reuters.com/business/finance/us-consumer-watchdog-probes-major-us-banks-over-zelle-scam-wsj-reports-2024-08-07/) that the Consumer Financial Protection Bureau was investigating several banks due to their handling of Zelle.
On December 20, 2024, The Consumer Financial Protection Bureau (CFPB) responded by [filing](https://files.consumerfinance.gov/f/documents/cfpb_Zelle-Complaint_2024-12.pdf) a lawsuit against Early Warning Services, LLC and the major banks including Bank of America, JPMorgan Chase, and Wells Fargo. The CFPB alleges that these institutions prioritized the rapid deployment of Zelle over implementing effective anti-fraud measures, resulting in significant consumer losses. The lawsuit contends that the defendants failed to adequately address these issues, often denying relief to defrauded consumers. The CFPB seeks injunctive relief, monetary compensation for affected consumers, and civil penalties.
Just 5 days before the Senate Permanent Subcommittee on Investigations released its report, the [Aspen Institute](https://www.aspeninstitute.org/) Financial Security Program (Aspen FSP) [announced](https://www.aspeninstitute.org/news/task-force-on-fraud-and-scams/) the formation of a National Task Force for Fraud & Scam Prevention with their founding sponsor JPMorganChase and executive sponsor Zelle. The stated purpose of the Task Force is to develop a unified national strategy to help the U.S. government and private sector companies work together to stop fraud and scams. [Members](https://fraudtaskforce.aspeninstitute.org/membership) of this private/public task force include: JPMorgan Chase, Bank of America, Wells Fargo, Google, Meta, Amazon, Visa, Mastercard, Verizon, the Federal Trade Commission, the FBI Criminal Investigation Unit, US Department of the Treasury, Homeland Security, and many others.
The Aspen Institute is a 501(c)(3) nonprofit located in Washington DC. In [2023](https://projects.propublica.org/nonprofits/organizations/840399006) they had revenue of $232M and total assets of $519M with the primary source of income coming from donations and federal grants. Per their [mission](https://www.aspeninstitute.org/what-we-do/) statement, their goal is "realizing a free, just, and equitable society." The Institute works to achieve this through creating and driving policy as well as training future policy leaders.
Recently on November 25, 2024, FinCen [announced](https://www.fincen.gov/news/news-releases/fincen-joins-public-private-partnership-combat-fraud-and-scams-impacting) they are also joining the National Task Force that *"brings together key stakeholders including the financial services sector, technology companies, consumer advocacy groups, information sharing and analysis centers, and federal government agencies to develop a comprehensive national strategy for combating fraud and scams."* In The Case for a Coordinated National Strategy to Prevent Fraud and Scams, the Task Force lists [key components](https://fraudtaskforce.aspeninstitute.org/time-is-now) of a national strategy to include improved education of consumers to identify fraud, enhanced information sharing across industry, law enforcement, and regulatory agencies by use of data exchanges and legal mechanisms for sharing information. As well as empowering law enforcement with additional authority and resources. The document cites the recent [UK action](https://www.gov.uk/government/news/new-powers-to-seize-cryptoassets-used-by-criminals-go-live) as an example of recent amendments to law enforcement powers which in England means police will no longer be required to arrest seizing crypto from a suspect, can seize written passwords or memory sticks, as well as transfer "crypto assets" to a law enforcement wallet.
In an August 2024 [interview](https://www.businessinsider.com/zelle-scams-how-to-get-money-back-2024-8?) with Fortune, Ben Chance, the Chief Fraud Risk Management Officer for Early Warning Services reportedly "told the outlet that the best way to prevent scams on money-sharing apps is better user education, sound policy and more funding for law enforcement." This sounds very similar to the National Strategy to Prevent Fraud and Scams being crafted by the National Task Force for Fraud & Scam Prevention, with more user education and law enforcement. No mention of standardized reimbursement policies or enhancing transparency around fraud investigations which are the primary accusations aimed at Zelle and its owners by the US Senate and the subject of the current investigation by the Consumer Financial Protection Bureau.
-

@ d61f3bc5:0da6ef4a
2025-02-12 16:57:44
Micropayments on the Internet have been theorized for decades. However, it wasn’t until the emergence of Nostr that we’ve finally seen them deployed at scale. Nostr is still in its infancy, yet we are already witnessing an explosion of apps built on top of this open protocol. And most of them are featuring zaps! With the recent Primal 2.1 release, Nostr developers now have the option to enhance the experience for their users by integrating a Nostr-powered bitcoin wallet.
There is no doubt that micropayments add a new dimension to consumer apps. The incumbents have realized this and are rushing to add payments to their closed platforms. It won't be long before apps that don’t include built-in payments feel dated or outright broken. The question is not if apps of the future will have built-in payments, but what *kind* of payments they will be. Given that open networks have a tendency to win, our bet is that apps of the future will be powered by Bitcoin. Let’s see how Primal can help.
## Primal Wallet
Our vision for Primal Wallet is simple: deliver the smoothest transactional bitcoin wallet, endowed with expert Nostr skills. The wallet leverages Nostr’s open social graph as a de facto public lightning directory, while offering the highest level of user experience for Nostr’s rich content. For example, the user can scroll through the transaction list, select a zap, and drill straight into the conversation thread where the zap originated. The whole flow feels perfectly natural.

Since we launched Primal Wallet in December 2023, the user response has been incredibly positive. People love the idea of being able to post something on Nostr, get zaps from plebs around the world, then buy a coffee or a meal with those sats - all from the same app.
Having a bitcoin wallet with social skills resonated strongly with users, so Primal Wallet grew rapidly in popularity and usage. Since the launch, we have processed **1,338,460** transactions, with **238,916** just in the past month alone. This rivals some of the leading bitcoin wallets, and we are just getting started! We hear from many bitcoin OGs that they are using Primal Wallet as their transactional daily driver. Bullish.
All this is great, but something has been missing. Our users demanded the ability to connect Primal Wallet to other Nostr apps, so they can zap from anywhere in Nostr’s growing ecosystem.
## Zapping from Any Nostr App
For an existing Primal user, connecting the wallet to a new Nostr app can now be done in two clicks. Let’s take a look at how this is done from Olas, one of the most exciting new apps on Nostr:

Yes. Click, click. And you can start zapping!
Such smooth integration of payments is not available in any competing technology stack. Tradfi, fintech, crypto, etc., have nothing on Bitcoin and Nostr. Two clicks and your external wallet is connected. I’ll give you a moment now to allow for this new reality to settle in.
Primal enables you to connect any number of external apps and manage them from wallet settings:

Note that you can set your daily spend budget for each app or revoke its access at any time.
## How This Works
So, what is this sorcery? How does it work under the hood?
Connecting Nostr apps to external wallets is accomplished via the Nostr Wallet Connect protocol. It utilizes Nostr’s public relay infrastructure to enable communication between apps and wallets. You can learn more about this protocol [here](https://nwc.dev/), and access developer docs [here](https://docs.nwc.dev/).
The smooth, two-click connection setup UX is implemented through deep links between Primal and the external app. Here’s the deep link that the external app needs to call to invoke this feature:
```nostrnwc+primal://connect?appicon=[icon_url]&appname=[app_name]&callback=[callback_string]```
After the user clicks “Create Wallet Connection” in Primal, the Primal app calls the deep link defined in the callback, and passes the NWC connection string. That's all that the external app needs to make the wallet connection.
## What Comes Next?
The Nostr Wallet Connect protocol has been around for almost two years. Several bitcoin wallets implement it and many Nostr apps use it as their main way of enabling payments. What’s new with Primal 2.1 is the elevated user experience. Since Primal is a Nostr-powered wallet, it is aware of all the relevant metadata for each transaction: Nostr zaps, users, and the related events. Primal indexes the entire Nostr network, and now this is open to all Nostr apps that wish to integrate payments.
Nostr keeps expanding and getting better. Its openness enables us to build capabilities that lift all boats. The future is bright; I can’t wait to see how things evolve from here. 🍿🍿🍿
-

@ 94a6a78a:0ddf320e
2025-02-12 15:05:48
Azzamo is more than just a relay provider—it’s a **high-performance network** designed to make Nostr **faster, smoother, and more reliable** for everyone. Whether you're **posting notes, zapping sats, sharing media, or sending DMs**, Azzamo keeps your Nostr experience **seamless and efficient**.
Nostr is unstoppable, but **not all relays are the same**. Some are **slow, unreliable, or disappear overnight**, while others get **overloaded**, making message delivery **inconsistent**. Azzamo is built differently—offering **fast, stable, and globally distributed relays** to ensure **low-latency, high-speed connections**, no matter where you are.
---
## **🌍 Premium Relays for Maximum Performance**
Azzamo **Premium Relays** are optimized for **speed, reliability, and uptime**, available exclusively to **Premium users**:
📡 **Azzamo Premium Relays:**
- **Europe:** `wss://relay.azzamo.net`
- **America:** `wss://us.azzamo.net`
- **Asia:** `wss://asia.azzamo.net`
Add **Azzamo Premium Time** to **unlock unlimited, high-speed access** across these global relays.
🔗 **Get Premium:** [azzamo.net/premium](https://azzamo.net/premium)
---
## **🆓 Freemium Relays – Free for Everyone**
Azzamo believes in **keeping Nostr open** and accessible to all. That’s why we offer **free relays for everyone**, with **no rate limits for Premium members**
📡 **Freemium Relays:**
- **Free Relay:** `wss://nostr.azzamo.net` – Open to all.
- **Inbox Relay:** `wss://inbox.azzamo.net` – Reliable for DMs & group messages.
By offering both **free and premium options**, Azzamo ensures that **anyone can use Nostr, while also funding the infrastructure that keeps it running smoothly.**
---
## **🛡️ Minimal Moderation, Maximum Transparency**
Nostr is about **free speech**, but that doesn’t mean **zero moderation.** Azzamo follows a **minimal moderation policy** to keep relays **functional and spam-free** while maintaining **transparency** in enforcement.\
\
🚫 **Spam & network abuse**\
🚫 **Illegal content (CSAM, fraud, malware, scams)**\
🚫 **Impersonation & identity abuse**
We also maintain a **public Ban API** for **transparent moderation decisions**.
📖 **More on our Ban API:** [azzamo.net/introducing-the-azzamo-ban-api](https://azzamo.net/introducing-the-azzamo-ban-api)
---
## **🚀 Get Started with Azzamo Relays Today!**
🔗 **Connect now:**\
📡 `wss://nostr.azzamo.net` (Freemium Free Relay)\
📬 `wss://inbox.azzamo.net` (Freemium Inbox Relay)\
📡 `wss://relay.azzamo.net` (Premium Europe Relay)\
📡 `wss://us.azzamo.net` (Premium Americas Relay)\
📡 `wss://asia.azzamo.net` (Premium Asia Relay)
Nostr is growing fast. **Make sure your relays can keep up.** 🚀
#azzamo #grownostr #nostr #relay #relays #premiumrelay #paidrelay
-

@ 3b7fc823:e194354f
2025-02-12 01:15:49
We are constantly surrounded by technologies that claim to enhance our experiences but often come at the cost of our privacy. Think about it – every time you visit a website, cookies are being dropped like breadcrumbs, tracking your every move without you even knowing.
**How Tech Companies Collect Your Data: The Spy Next Door**
1. **Cookies**: These tiny files are placed on your device as soon as you visit a site. They follow you around the web, creating a digital trail that companies use to learn about your habits and interests.
2. **Tracking Pixels**: Like cookies, these are invisible tags that track your actions across different websites. Imagine someone following you wherever you go online – that's what tracking pixels do.
3. **Behavioral Targeting**: This is when companies analyze your browsing history to serve you ads tailored to your interests. It's like knowing what you like and then bombarding you with it, whether you like it or not.
4. **Data Brokers**: These middlemen collect data from various sources and sell it on to the highest bidder. Your information could be used for marketing, insurance, or even political purposes – without your consent!
5. **Third-Party trackers**: Apps and websites you visit may share your data with other companies, creating a web of surveillance that's hard to escape.
**What They Do with Your Data**
Once companies have your data, they can use it for targeted advertising, profile building, and even political manipulation. Think about the Cambridge Analytica scandal... Your data isn't just used to make your experience better; it's being sold and exploited in ways you probably never imagined.
**How to Stop Them: Empower Yourself**
1. **Use Privacy-Friendly Browsers**: Tools like Brave or Firefox with enhanced tracking protection can block trackers and cookies, giving you control over what data is collected.
2. **Block Trackers and Cookies**: Browser extensions that allow you to block these elements are available for free, providing an added layer of privacy.
3. **Minimize Data Usage**: When using apps or websites, avoid granting unnecessary permissions that could lead to data collection.
4. **Delete Unused Apps**: Regularly delete apps and services that are no longer needed to stop data collection from inactive accounts.
5. **Read Privacy Policies**: Before accepting terms of service or privacy policies, read through them to understand what data will be collected and how it will be used.
6. **Use Incognito or Private Browsing Modes**: These modes often block cookies and trackers, offering an additional way to reduce data collection. But remember that Google was still tracking you on Chrome regardless, so your mileage may vary.
7. **Limit Device Usage**: Avoid using personal devices for sensitive activities when privacy is a concern.
8. **Use Tor**: Yes it's slower, yes some sites won't work. It's more private and you using helps disquise traffic giving protection for others that might need it more than you do.
**Why It Matters: The Domino Effect**
The data collected today isn't just for ads; it's used in decision-making processes that can affect your life. From insurance rates to job opportunities, your data can influence significant aspects of your existence. Imagine a world where your information is bought and sold without your consent – it's time to take control.
**Your Data, Your Choice**
Your data is being collected and sold without your consent, and the time to act is now. By understanding how data collection works and taking steps to protect yourself, you can reclaim control over your privacy. Remember, you're not just a user – you're the owner of your information. It's time to stand up for your rights and demand transparency from the companies that claim to serve you.
**Don't Let Corporate Spies Steal Your Privacy**
Your data is valuable, and it's being harvested without your knowledge. Take action today by educating yourself and others about the importance of privacy. Together, we can create a world where privacy is respected and protected, not exploited for profit.
Join the movement to fight against corporate surveillance and protect your right to privacy. Your information is too important to leave in the hands of those who don't have your consent. It's time to take a stand – your digital life depends on it.
---
Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero
82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
-

@ dc4cd086:cee77c06
2025-02-09 03:35:25
Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content.
## Key Features:
### Video Processing:
- Automatically downloads YouTube videos, transcripts, and chapter information
- Splits transcripts into sections based on video chapters
### Content Summarization:
- Utilizes language models to transform spoken content into clear, readable text
- Formats output in AsciiDoc for improved readability and navigation
- Highlights key terms and concepts with [[term]] notation for potential cross-referencing
### Diagram Extraction:
- Analyzes video entropy to identify static diagram/slide sections
- Provides a user-friendly GUI for manual selection of relevant time ranges
- Allows users to pick representative frames from selected ranges
## Going Forward:
Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine.
Will support multiple open and closed language models for user choice
Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care.
While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs.
## Screenshots
### Frame Selection

This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection.
### Diagram Extraction

This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save.
## Links
- repo: https://github.com/limina1/video_article_converter
- Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE
## Output
And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately.
You can now view the article on #Alexandria
https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101
Initially published as chained kind 1's
nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn
Or view on Coracle
https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
-

@ 916a7ab7:146bb83e
2025-02-04 13:35:11
It was not ago that my life was simpler than it is today.
I remember being a simple clone, droning on through a structured life as I'd been trained to do since birth.
Like most people I knew, I was raised in a world where you were mentally prepared for a conceptually simple life:
1. Finish high school, if possible.
2. Go to college, if possible.
3. Find a job.
4. Earn money.
5. Pay bills.
6. Get married.
7. Start a family.
8. Pay more bills.
9. Raise family and (hopefully) launch the kids.
10. Plan to retire, but expect to work into your 70s.
It was a programmed formula for life. A generational blueprint, if you will. Sure, there would be unpredictable details, but I expected my life to follow this path.
As I plodded along through my fairly boring life, I checked most of those things off the list. High school was easy, but getting off the farm was not. Enlisting in the military solved that problem, and the pay in the mid-1990s wasn't bad for a 17 year old kid with no bills. I got paid every two weeks, lived in the barracks, and spent most of my money on booze. Life was good, and I had no other purpose than to do my job and keep earning money.
Before I knew it, though, everything changed. I got married, had some kids and accumulated a mountain of debt. Like my parents before me, I was stuck in a never ending cycle of working my ass off, paying bills, buying food, and trying to save what little money was left over for a future that was unpredictable at best. Financial struggles stressed our marriage, the kids continued eating more and more food, and then 2008 tanked the value of our home. That was the first nudge that stirred my oblivious slumber.
And there was more to come. Rising taxes, inflation, the clown show at the federal reserve, the wars funded by central banks, an astronomical national debt, and the burdens of our mistakes weighing down the futures of our children. Not to mention a federal government that actively seeks to censor, suppress, and financially imprison its own people. The times exuded chaos.
Then a few months ago, I woke up...
It happened during an episode of The Tuttle Twins, a cartoon show from Angel Studios. I homeschool my three youngest kids, and I'd let them watch TV during lunch so I could grade some papers. This cartoon was new to me, but the kids liked the music and the crazy raccoon. As fate would have it, they ended up watching an episode about Bitcoin. This, of course, led to a long series of questions:
"Dad, what's Bitcoin?"
"Is Bitcoin real?"
"Do you have Bitcoin?"
"Can I get Bitcoin for allowance instead of dollars?"
I had no answers for these questions, so we started doing some research together. We turned on our Chromebooks and launched a barrage of web searches. After reading a bunch of articles I came away with the idea that Bitcoin might be a real thing. Later that evening, and after the kids were in bed, I couldn't stop thinking about Bitcoin. I honestly didn't understand half of what I read in those articles, which bothered me. I'm not a super smart guy, but I catch on to things pretty quickly, and I wanted to better understand what I'd read. I expanded my search to podcasts and YouTube videos.
I ended up listening to a couple episodes from a Bitcoin Veterans podcast. As a veteran myself, I figured that this group of Bitcoin-savvy veterans would be able to help me figure out all this madness. I was right. I quickly learned that the word "Bitcoin" was just the tip of the iceberg, and I quickly found myself falling through an endless rabbit hole. They pointed me in a lot of different directions, but they were all helpful. (If you're a US military veteran and want to connect with this group, find them at [bitcoinveterans.org].)
A couple months ago, I couldn't tell you the difference between a Bitcoin and a meme coin. I'd come across the phrase Bitcoin mining, and I just thought there was a special group of people who mined a special metal to create coins with a big "B" on them. Why couldn't they just use the metal we already mined? Sheesh! I thought nostr was a virus, and a Kraken was still a giant squid.
As of today, I'm happy to say that I've made a little bit of progress. Those things above no longer confuse me, and I actually have a little bit of Bitcoin now. Sure, I'm still trying to wrap my head around NFTs and figure out who the Pepe frog man is, but I'm no longer completely lost. Not to mention, I just spent most of the last 24 hours figuring this whole nostr thing out, which excites me. I kind of missed the boat on the big name social media platforms, so I'm looking forward to this new decentralized approach to things.
For now, I'm just happy to be awake. Finally. I see the need for decentralization and the necessity of moving away from fiat monies. I don't have much to offer except my intellect and my love of writing, but I'm here to serve in any way that I can.
 @ 1c19eb1a:e22fb0bc
2025-03-03 19:14:42After my first major review of [Primal on Android](https://www.nostr-reviews.com/post/1733635103705/), we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client. Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity. It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub. If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings. Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in [NIP-55](https://github.com/nostr-protocol/nips/blob/master/55.md). Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber. This review of Amber is current as of version 3.2.5. 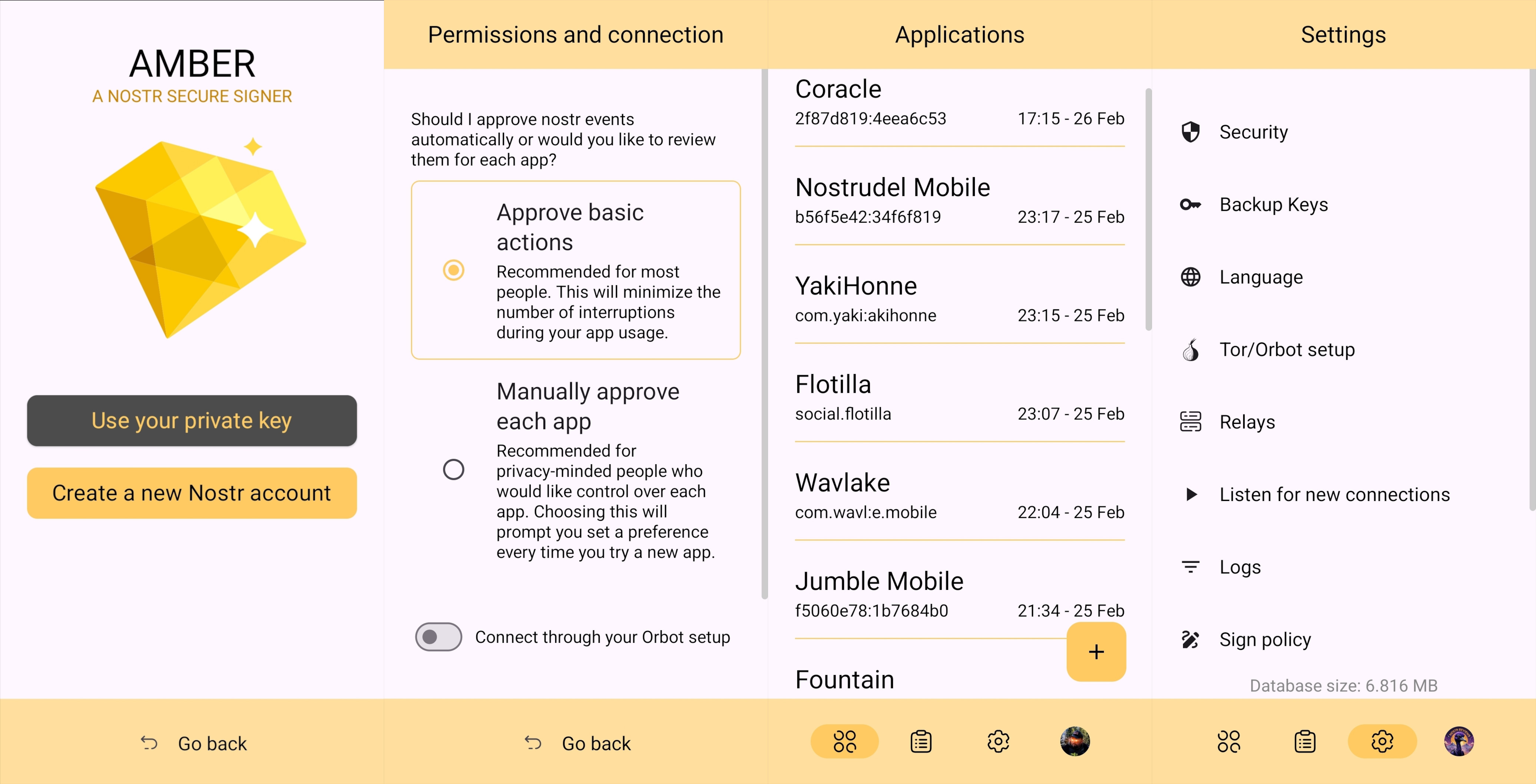 ## Overall Impression Score: **4.5** / 5 I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec. Despite being the only well-established Android signer available for Android, Amber ***can*** be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method ([NIP-07](https://github.com/nostr-protocol/nips/blob/master/07.md)) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing. A running list I created of applications that support login and signing with Amber can be found here: [Nostr Clients with External Signer Support](nostr:naddr1qvzqqqrcvgpzpde8f55w86vrhaeqmd955y4rraw8aunzxgxstsj7eyzgntyev2xtqydhwumn8ghj7un9d3shjtnzwf5kw6r5vfhkcapwdejhgtcpr4mhxue69uhkg6ttv95k7ue3x5cnwtnwdaehgu339e3k7mf0qq4xummnw3ez6cmvd9jkuarn94mkjarg94jhsar9wfhxzmpdwd5kwmn9wgkhxatswphhyaqrcy76t) I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either [NIP-55](https://github.com/nostr-protocol/nips/blob/master/55.md) or [NIP-46](https://github.com/nostr-protocol/nips/blob/master/46.md) login. I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn. nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time. ## Features Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control. ### Android Signing This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in. 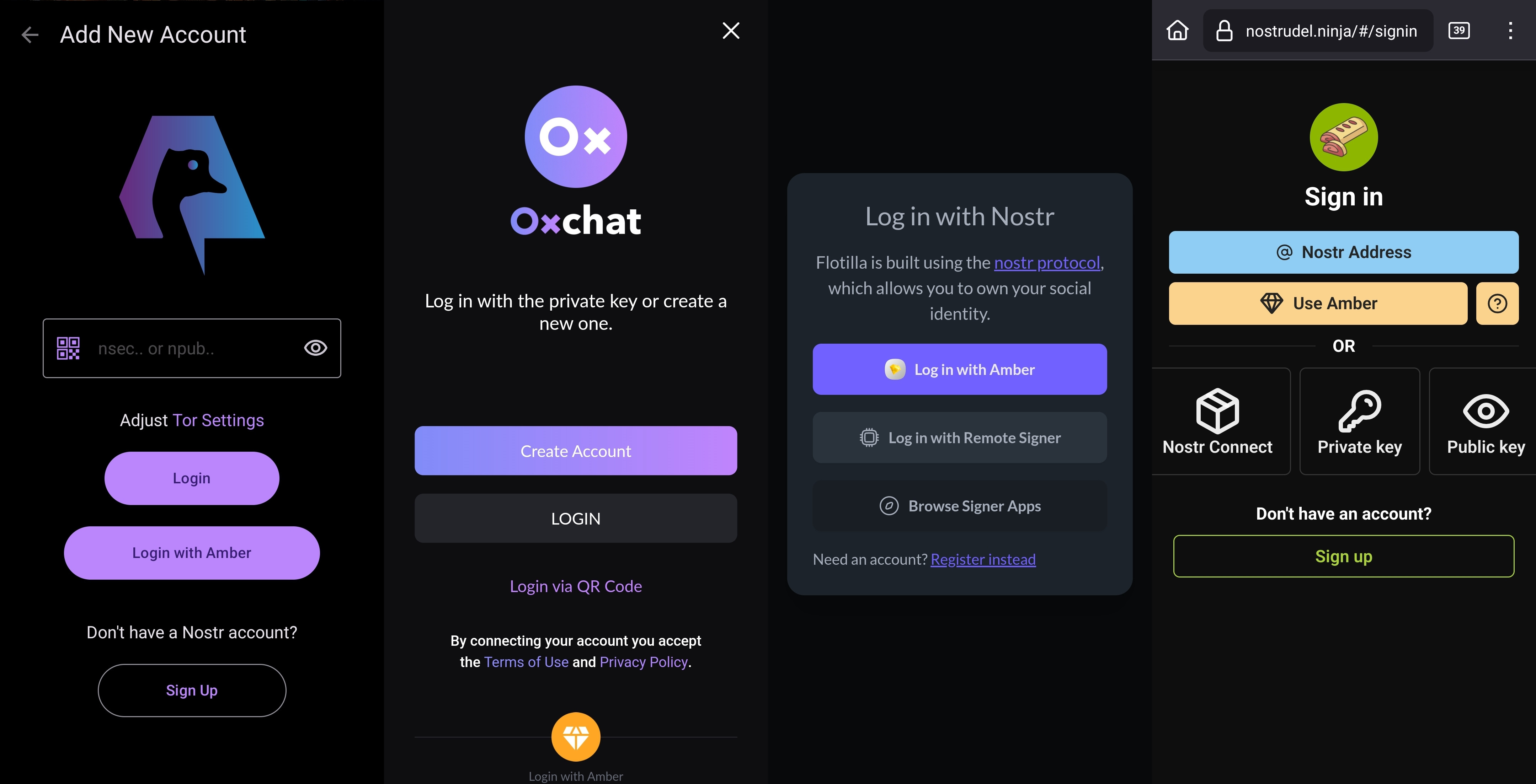 This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time. Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with. 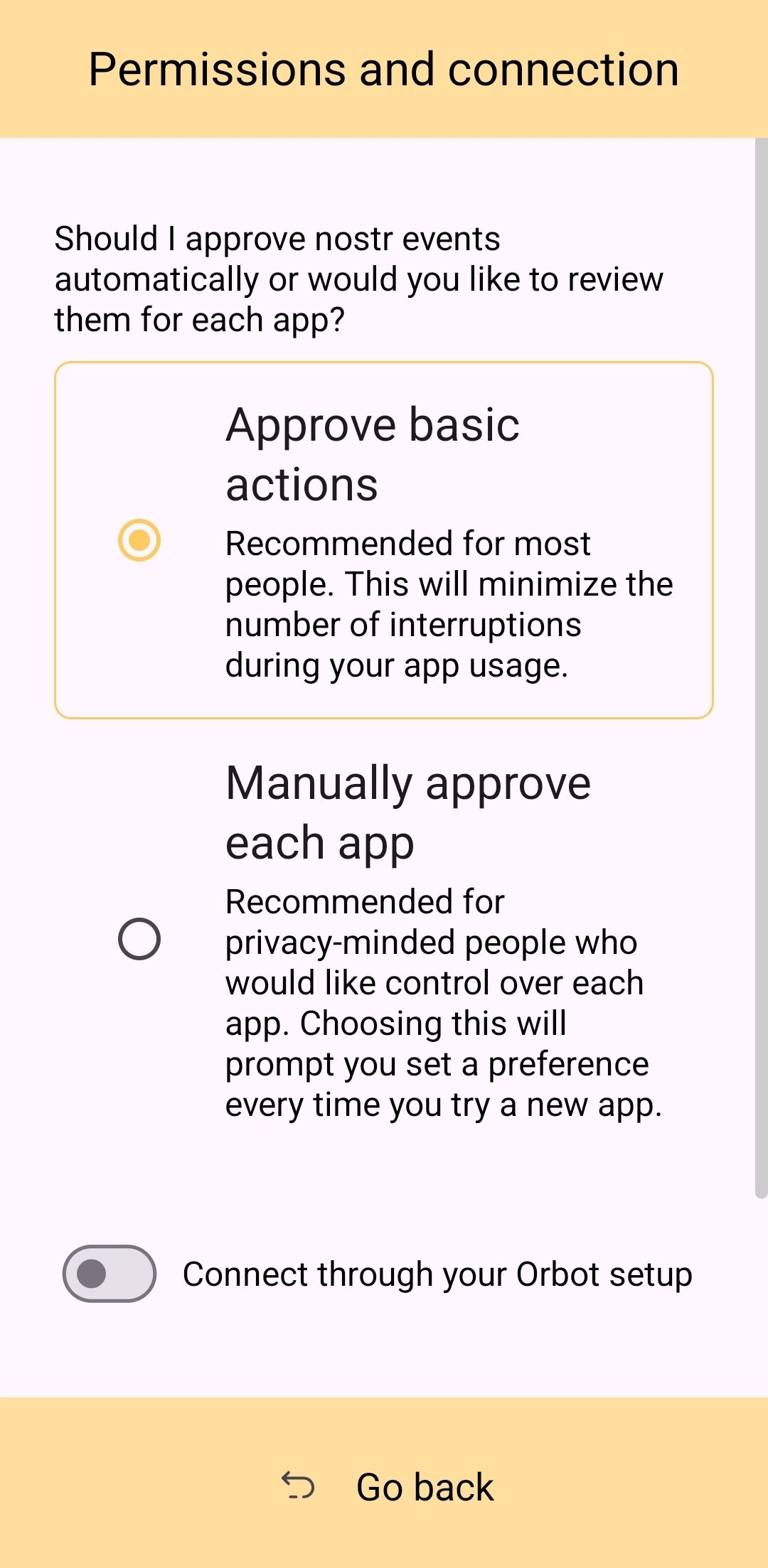 This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure. ### Nostr Connect/Bunker Signing This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable. Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected. 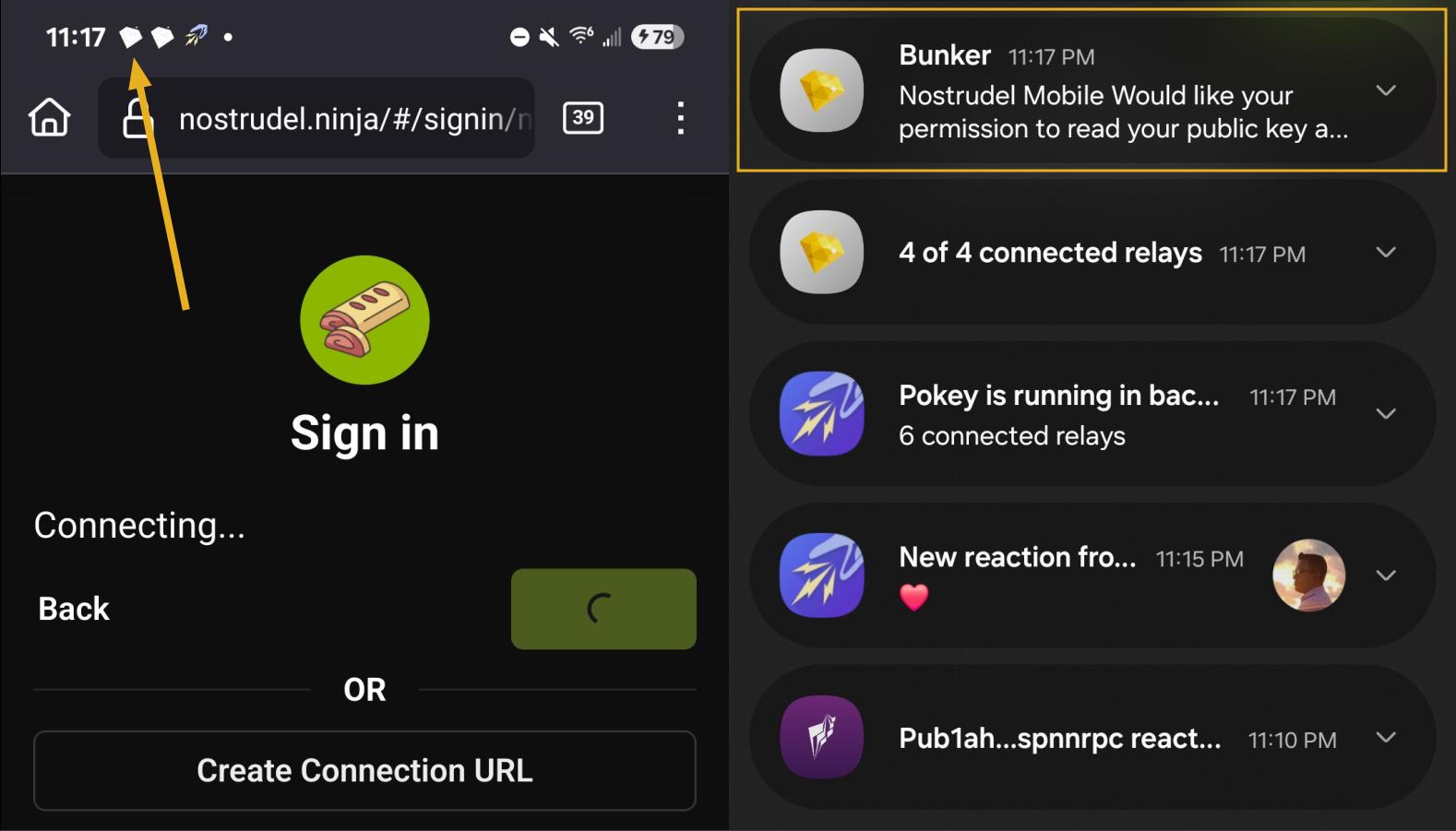 By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted. Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc. The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string. 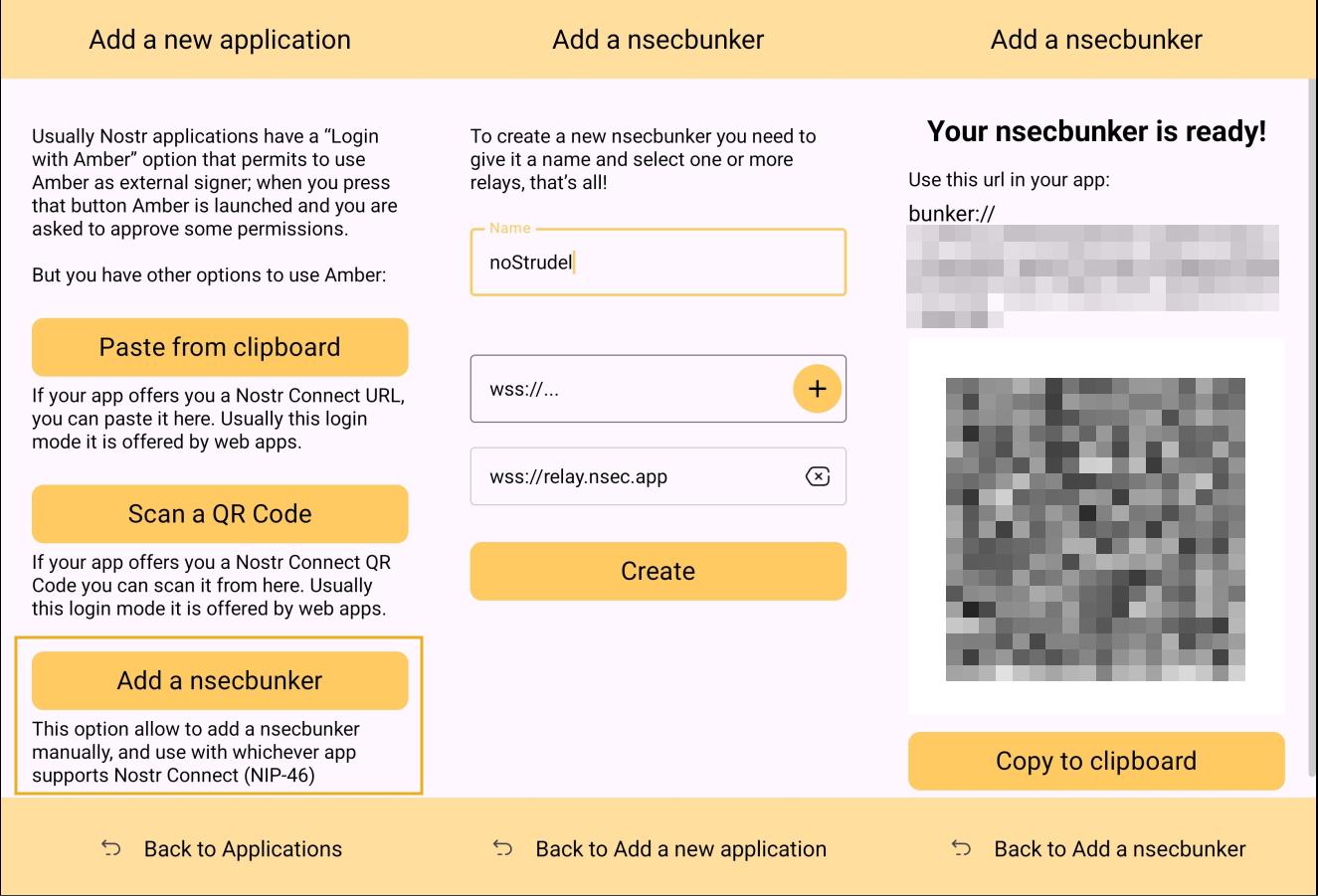 Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone. 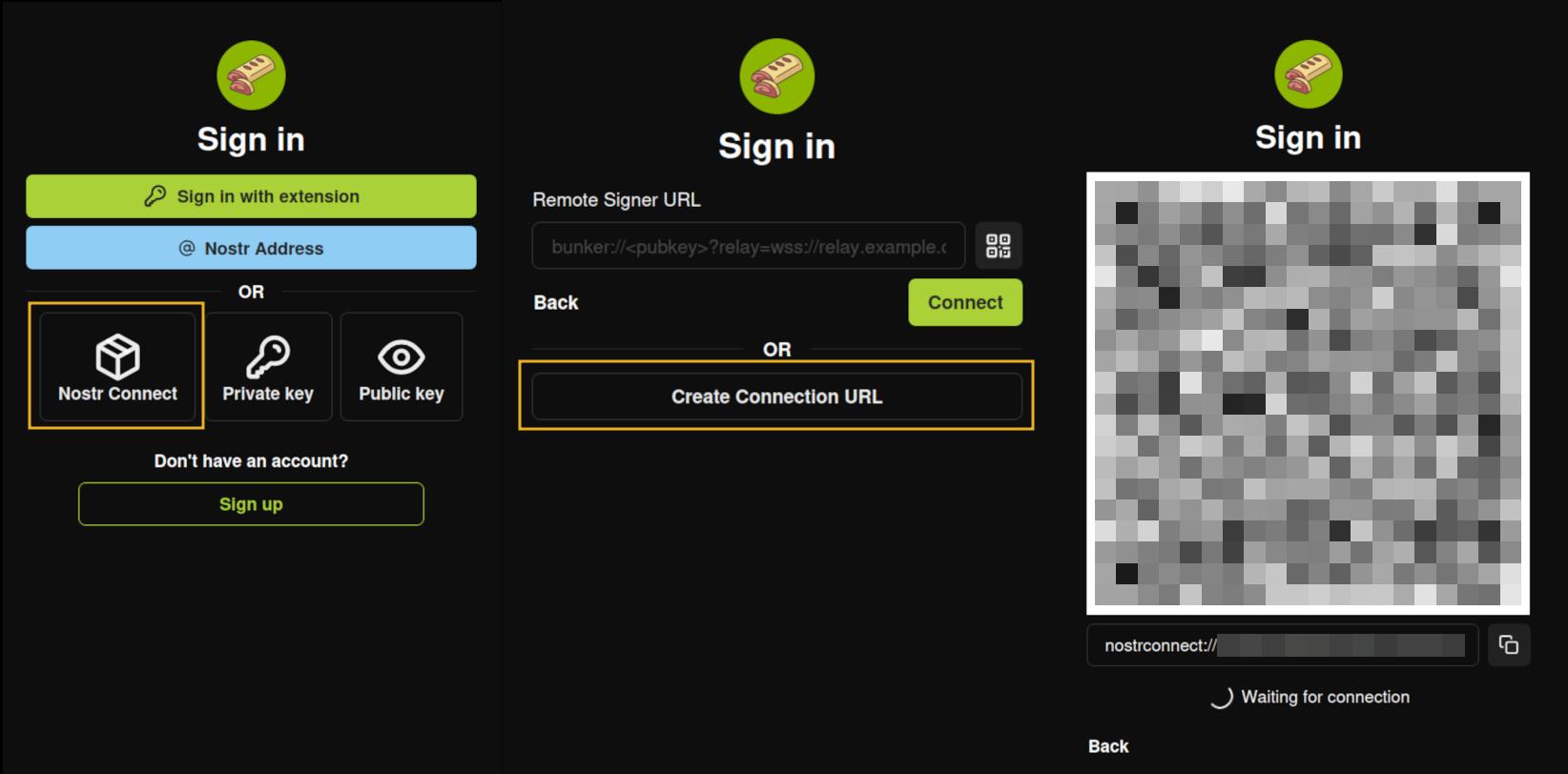 ### Multiple Accounts Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed. 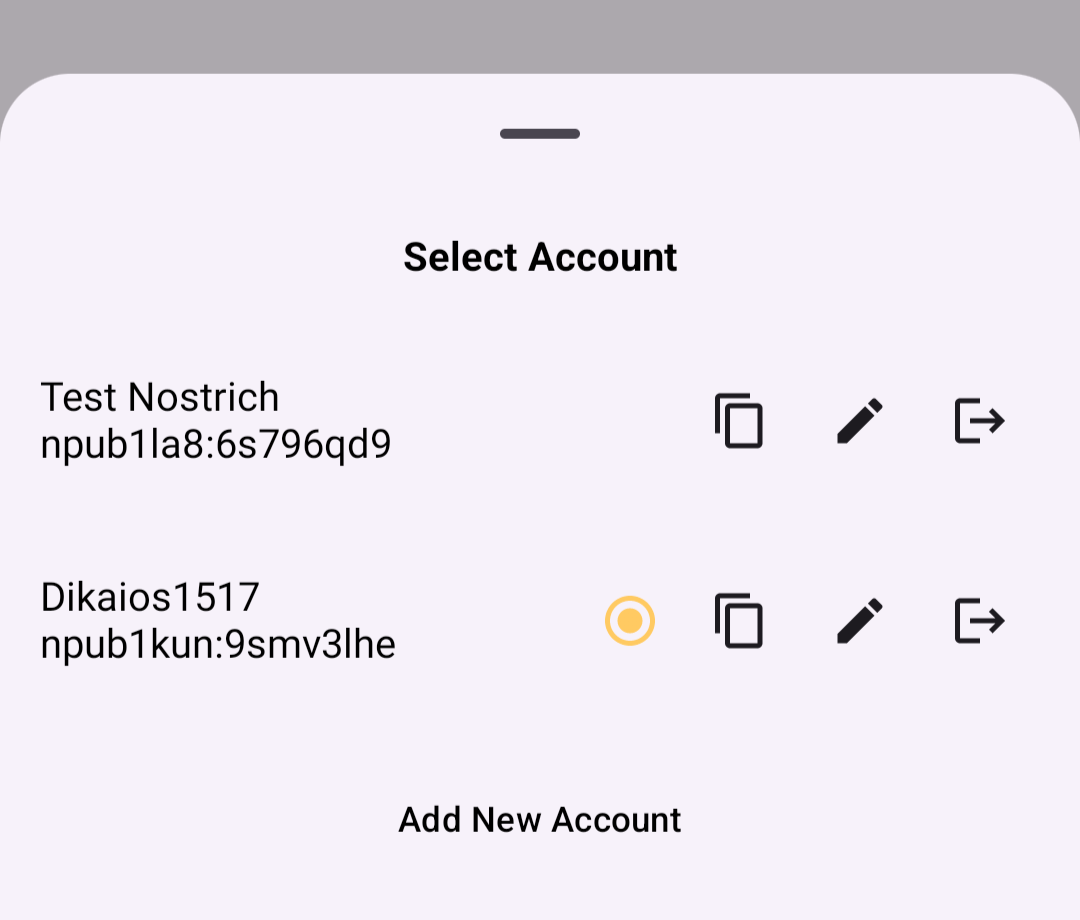 When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for. ### Key Backup & Restore Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec. 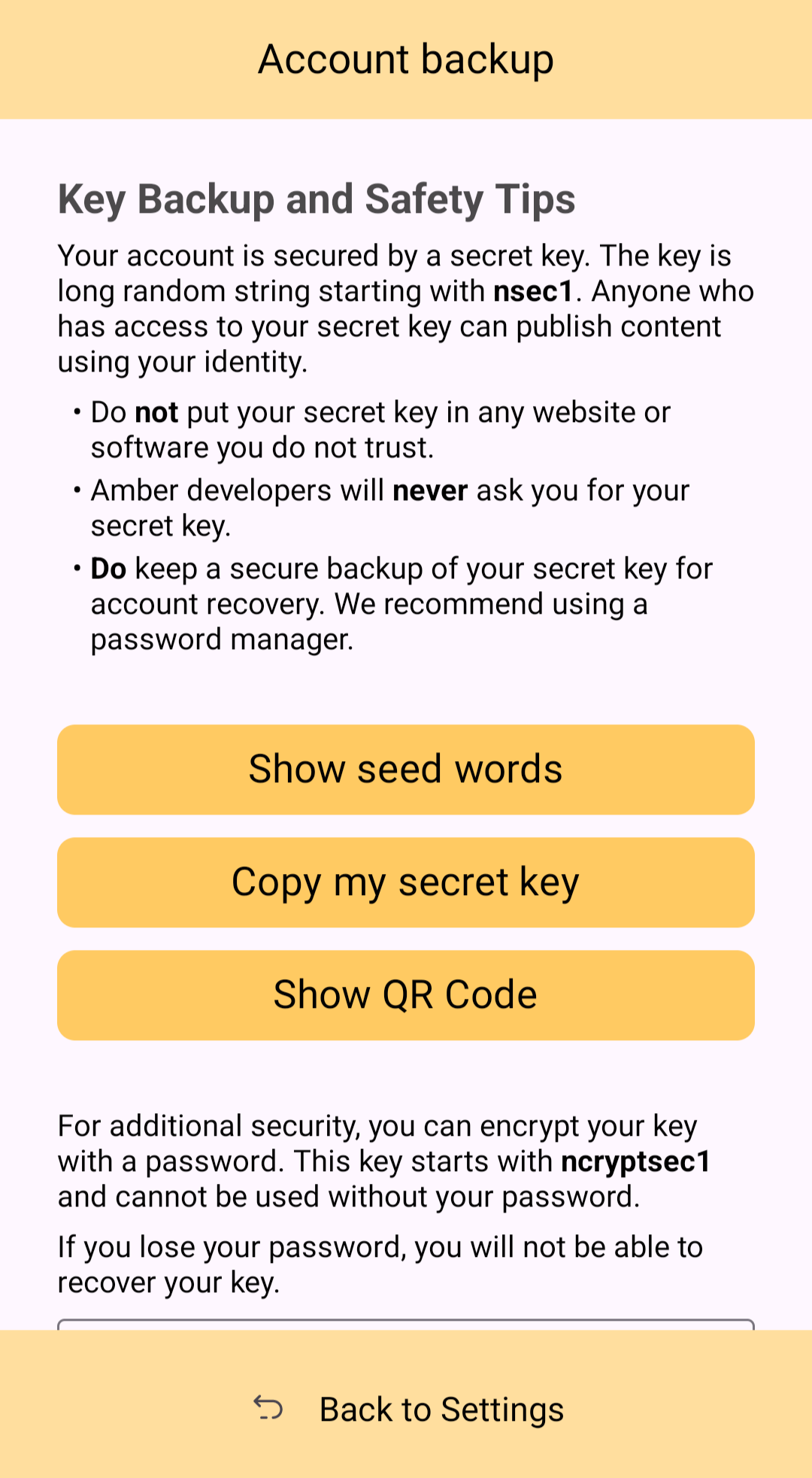 Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events. ### Tor Support While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity. 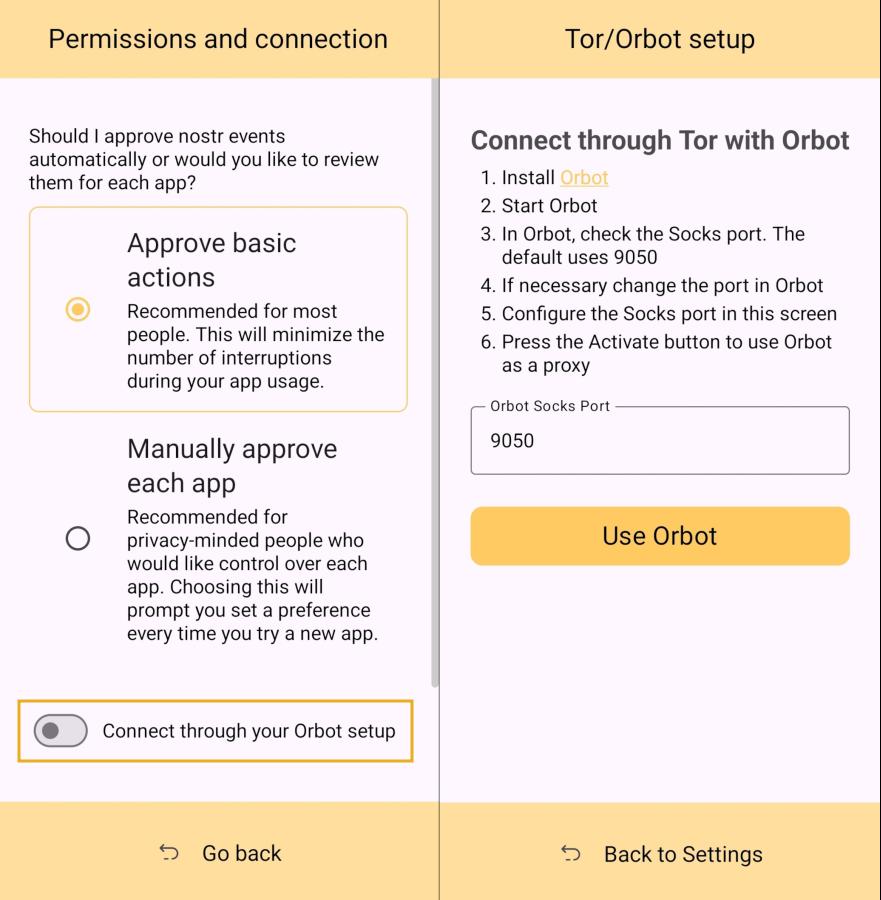 ### Additional Security Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access. ## Can My Grandma Use It? Score: **4.0** / 5 At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the ***same password*** for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs. That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touchpoint with Nostr, I think it holds up well, but could be somewhat streamlined. Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.  The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays. 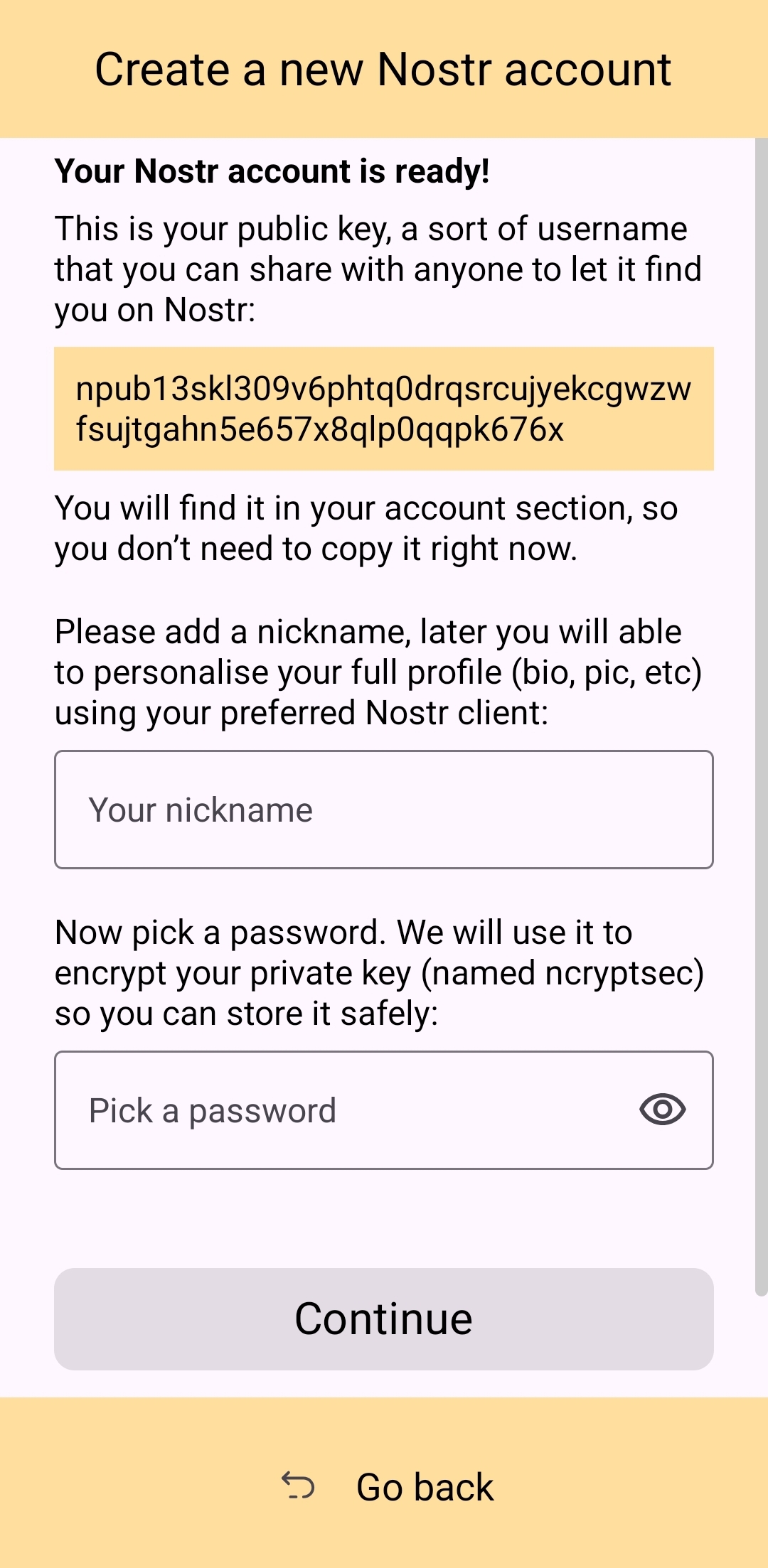 Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action. 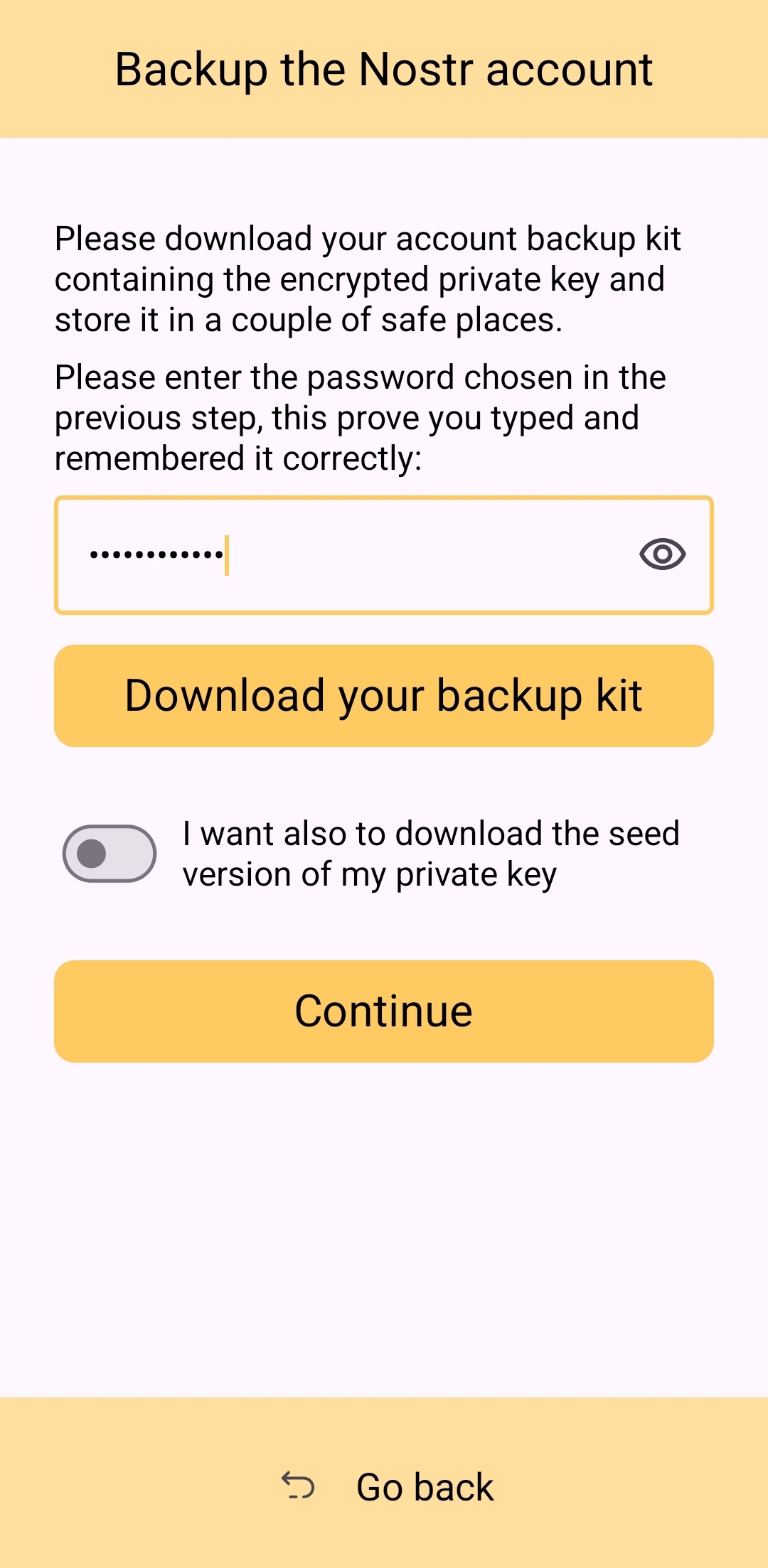 Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds. The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression. Now, I absolutely ***love*** the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process. Instead of: - Install Amber - Set up your keys - Install the client you want to use - Log in with Amber The process becomes: - Go to the Zapstore GitHub and download the latest version from the releases page. - Install the APK you downloaded, allowing any prompt to install unknown apps. - Open Zapstore and install Amber, allowing any prompt to install unknown apps again. - Open Amber and set up your keys. - Install the client you want to use - Log in with Amber An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store. ## How do UI Look? Score: **4.5** / 5 Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case. 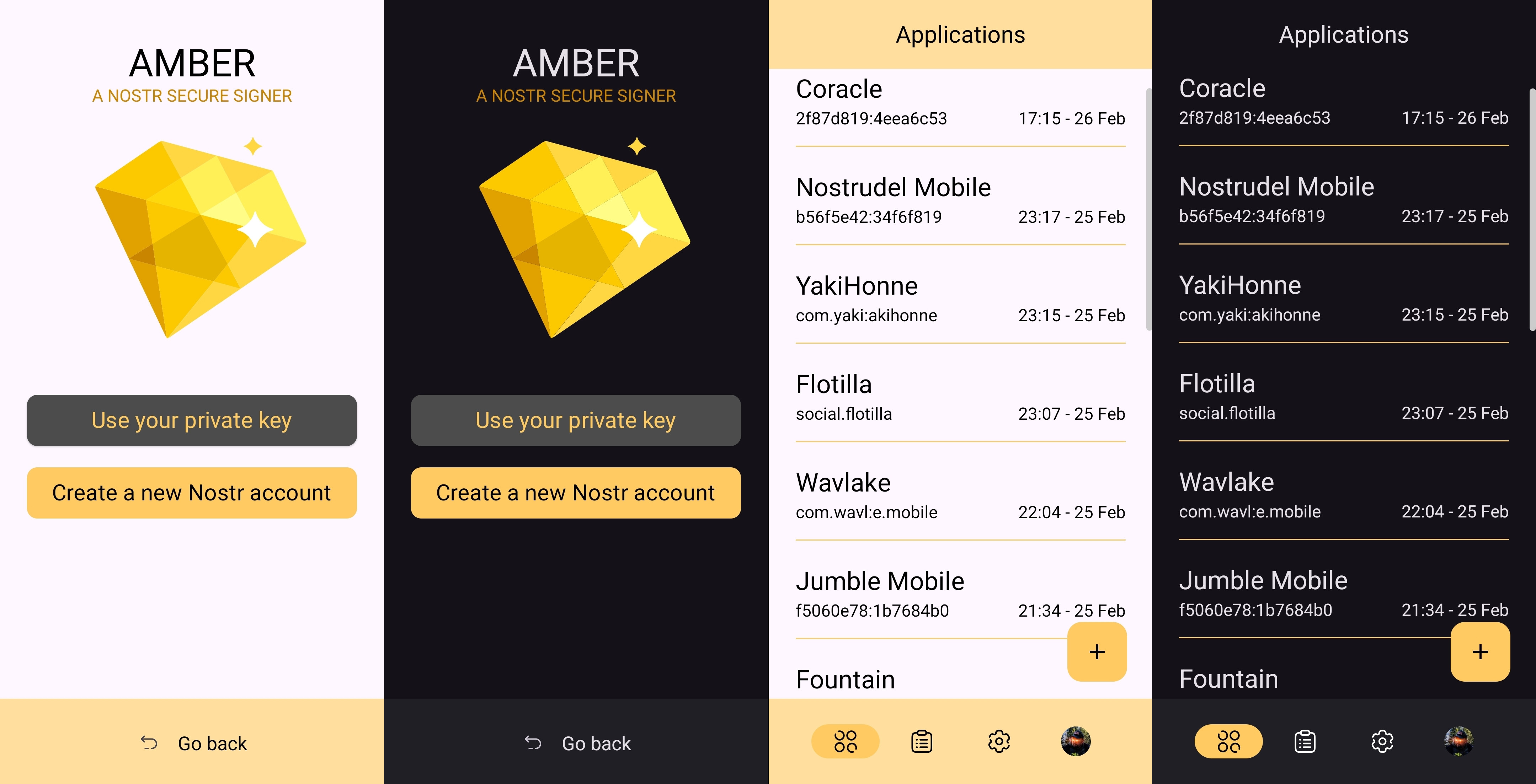 I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name. 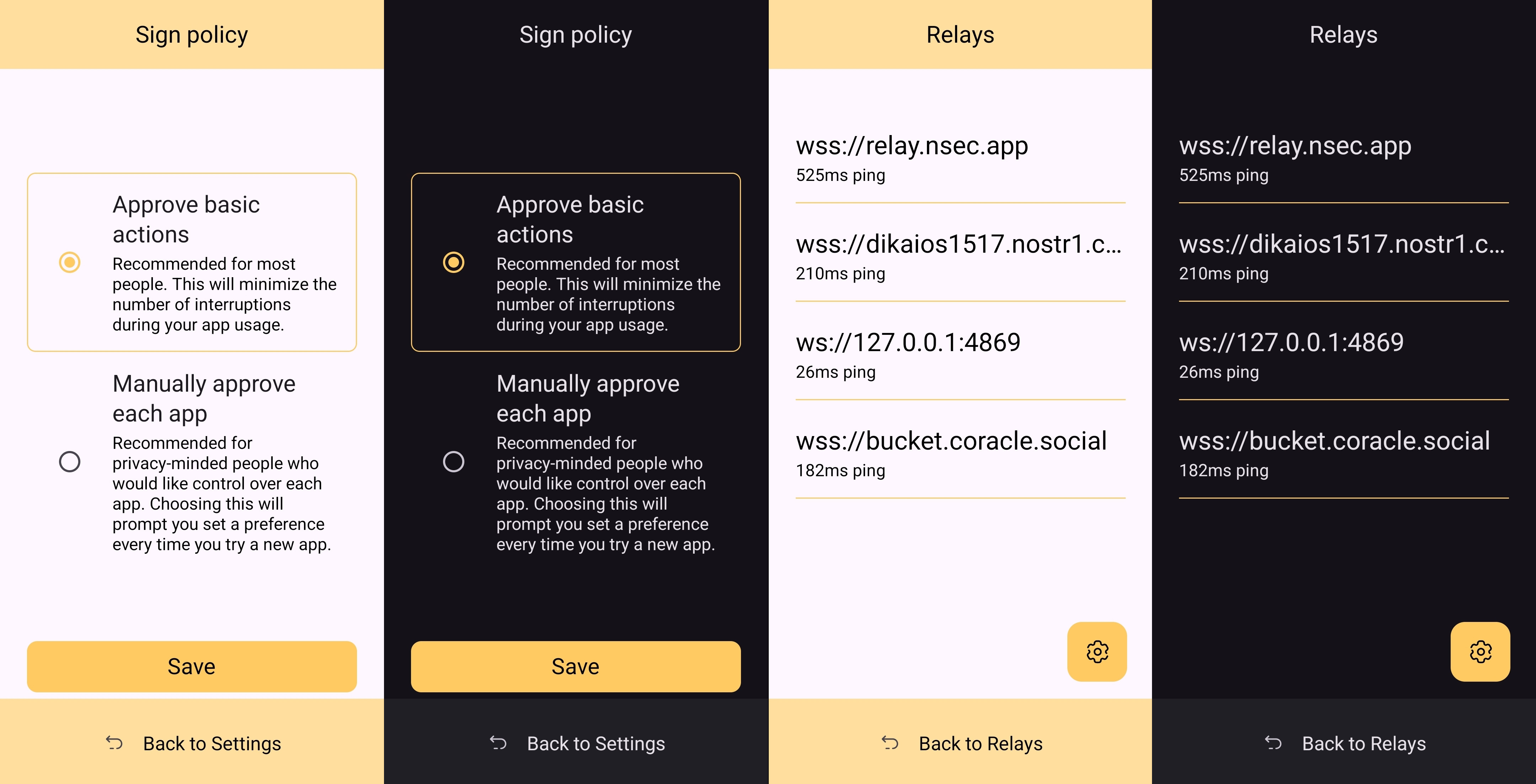 It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated. ## Relay Management Score: **4.9** / 5 Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture. In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings. 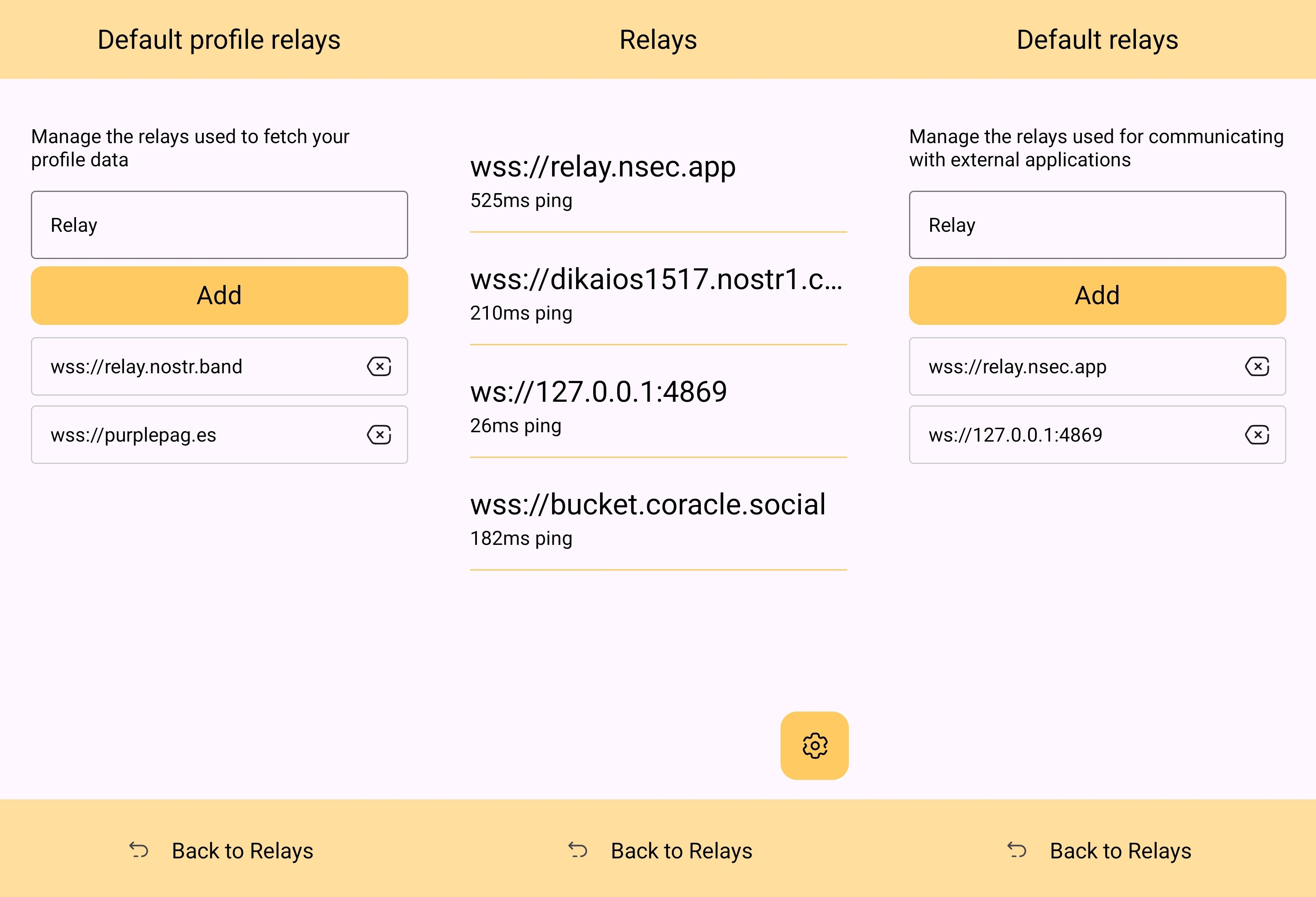 The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps. 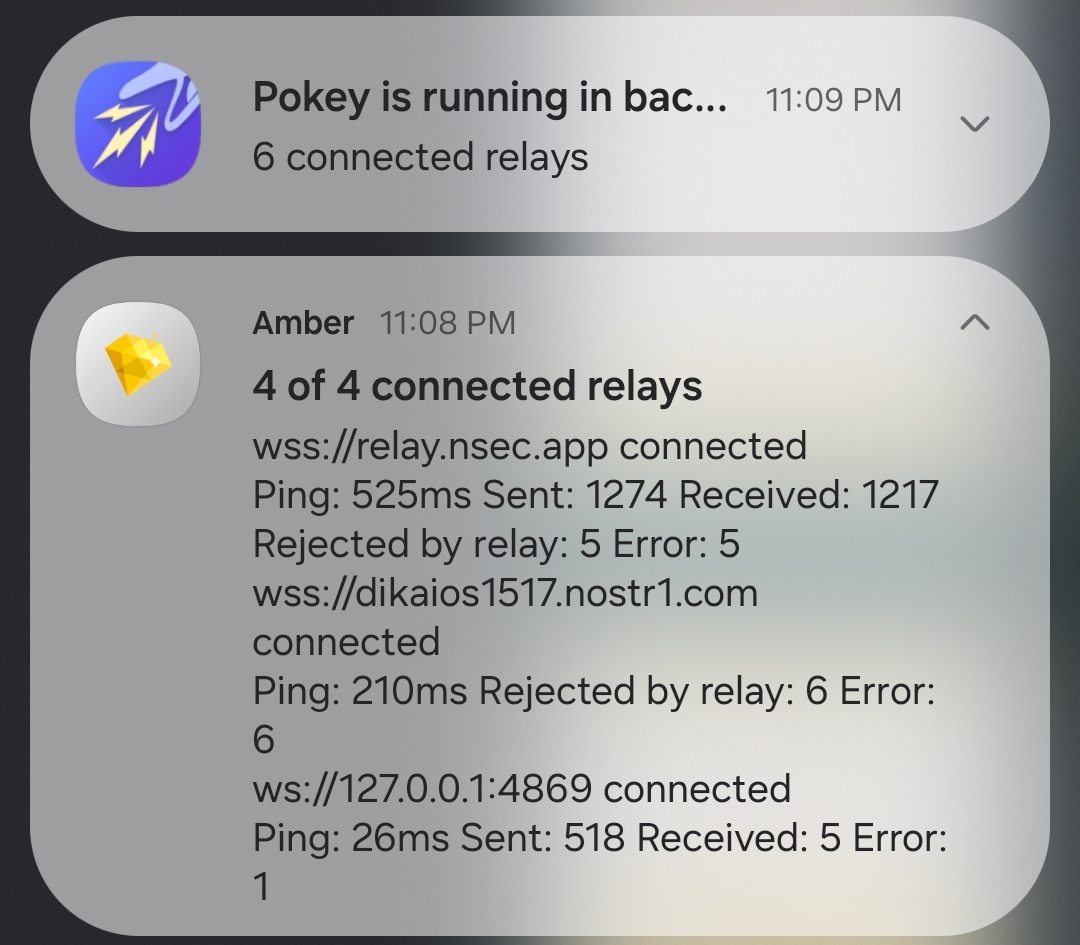 Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard. In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber. 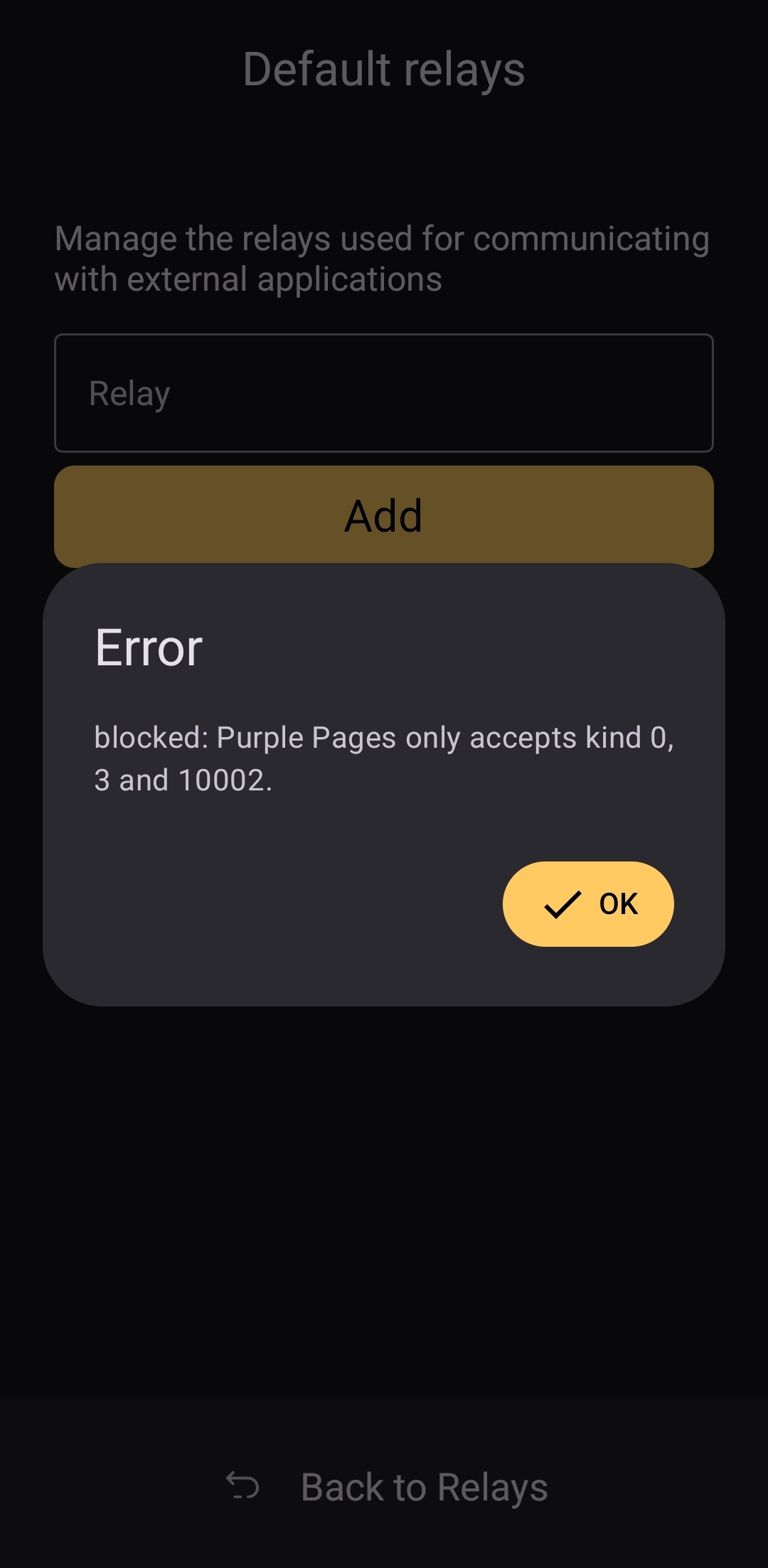 The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed. ## Current Users' Questions The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months. nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen. If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into. That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about ***how*** to use Amber, and that is a testament to Amber's ease of use all on its own. ## Wrap Up If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience. If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing. Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date! Now... What should I review next?
@ 1c19eb1a:e22fb0bc
2025-03-03 19:14:42After my first major review of [Primal on Android](https://www.nostr-reviews.com/post/1733635103705/), we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client. Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity. It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub. If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings. Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in [NIP-55](https://github.com/nostr-protocol/nips/blob/master/55.md). Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber. This review of Amber is current as of version 3.2.5. 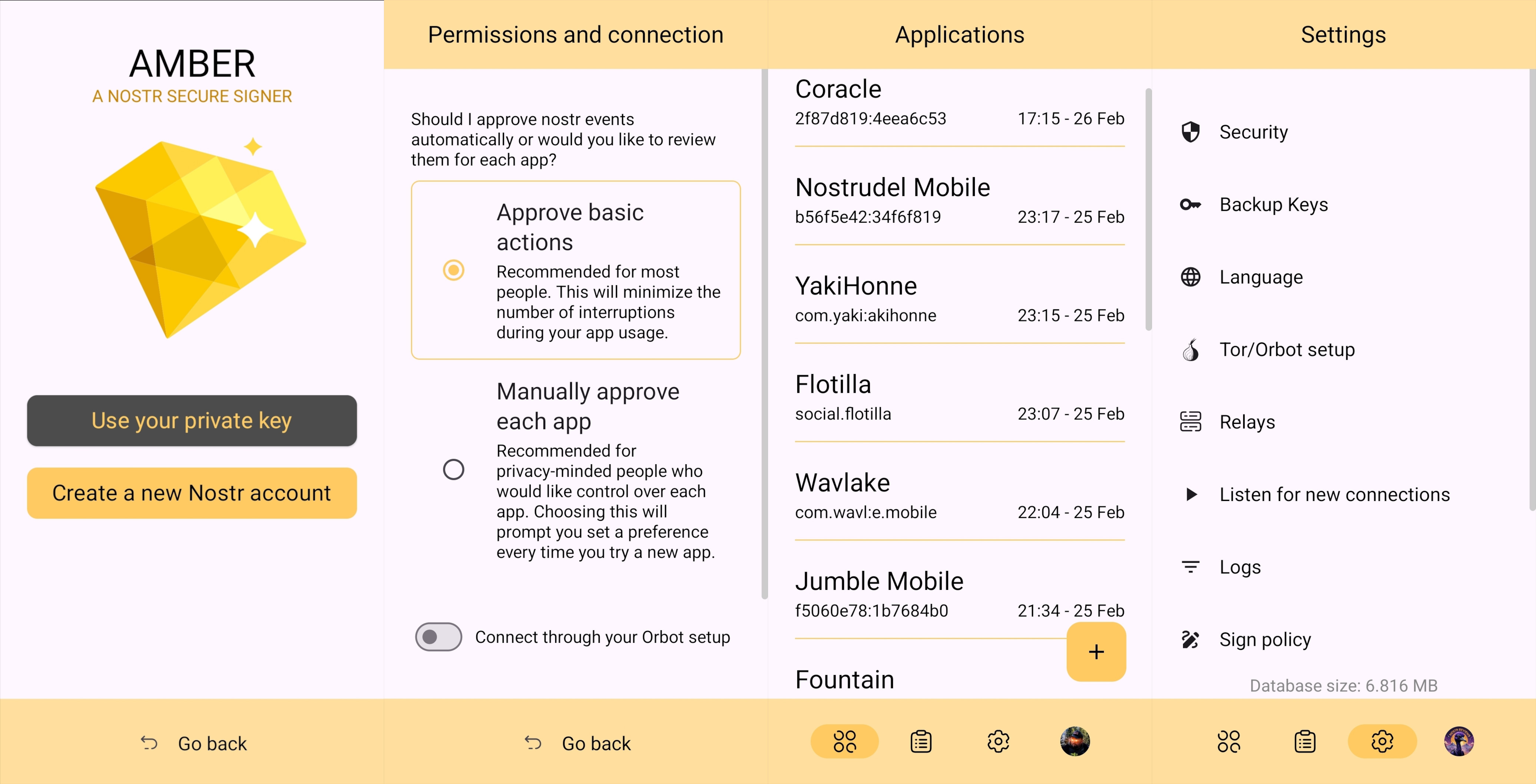 ## Overall Impression Score: **4.5** / 5 I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec. Despite being the only well-established Android signer available for Android, Amber ***can*** be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method ([NIP-07](https://github.com/nostr-protocol/nips/blob/master/07.md)) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing. A running list I created of applications that support login and signing with Amber can be found here: [Nostr Clients with External Signer Support](nostr:naddr1qvzqqqrcvgpzpde8f55w86vrhaeqmd955y4rraw8aunzxgxstsj7eyzgntyev2xtqydhwumn8ghj7un9d3shjtnzwf5kw6r5vfhkcapwdejhgtcpr4mhxue69uhkg6ttv95k7ue3x5cnwtnwdaehgu339e3k7mf0qq4xummnw3ez6cmvd9jkuarn94mkjarg94jhsar9wfhxzmpdwd5kwmn9wgkhxatswphhyaqrcy76t) I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either [NIP-55](https://github.com/nostr-protocol/nips/blob/master/55.md) or [NIP-46](https://github.com/nostr-protocol/nips/blob/master/46.md) login. I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn. nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time. ## Features Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control. ### Android Signing This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in. 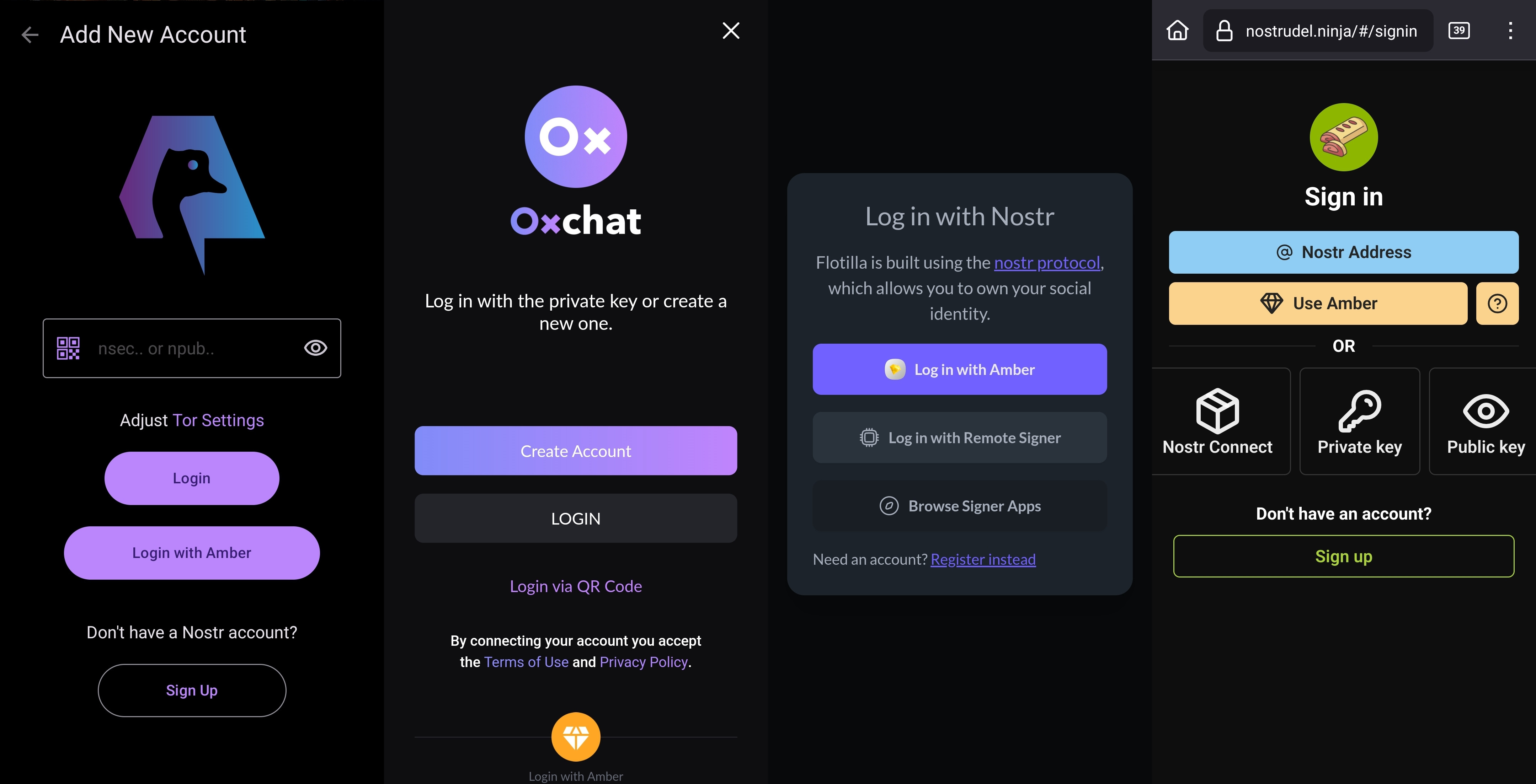 This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time. Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with. 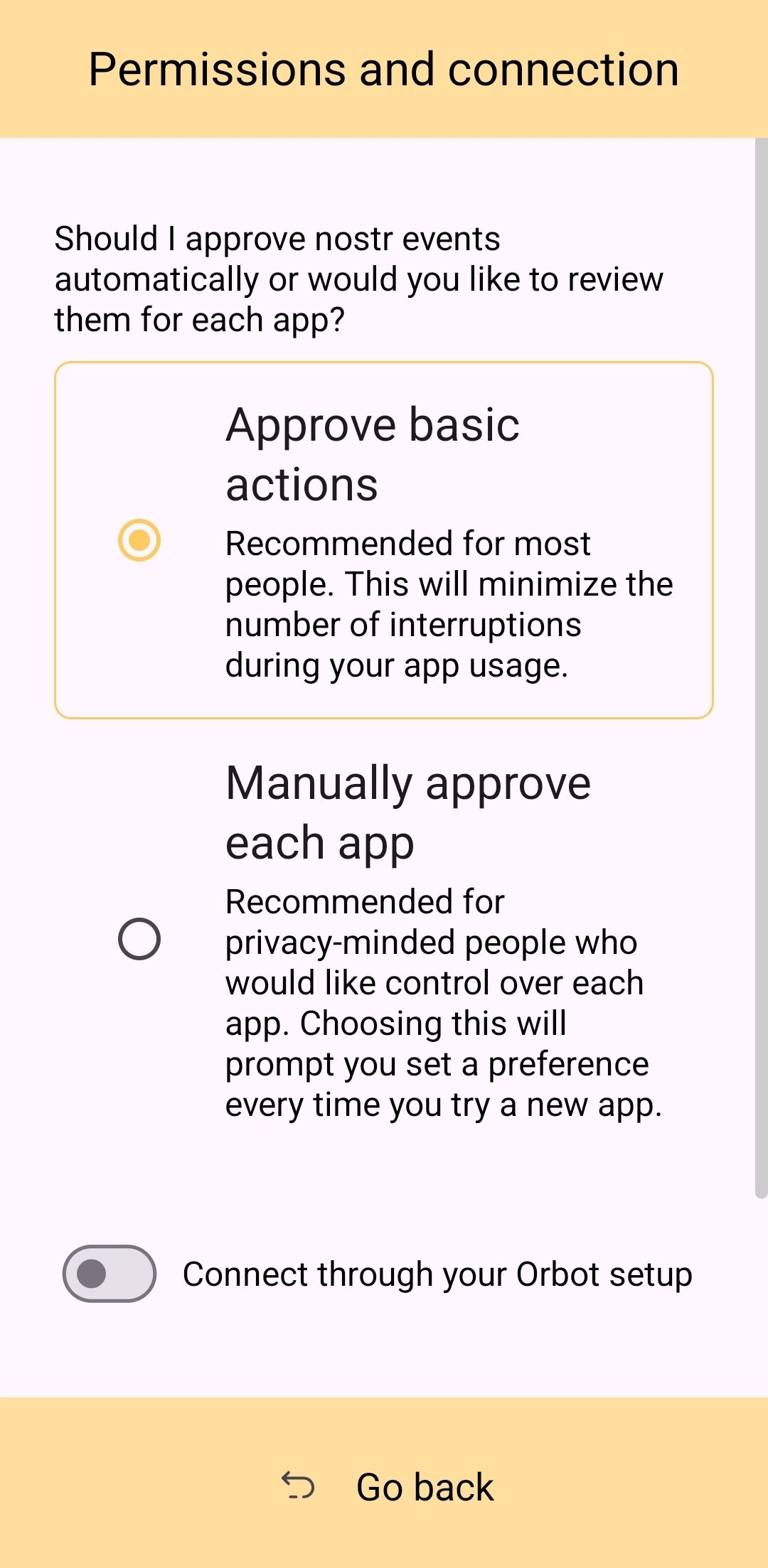 This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure. ### Nostr Connect/Bunker Signing This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable. Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected. 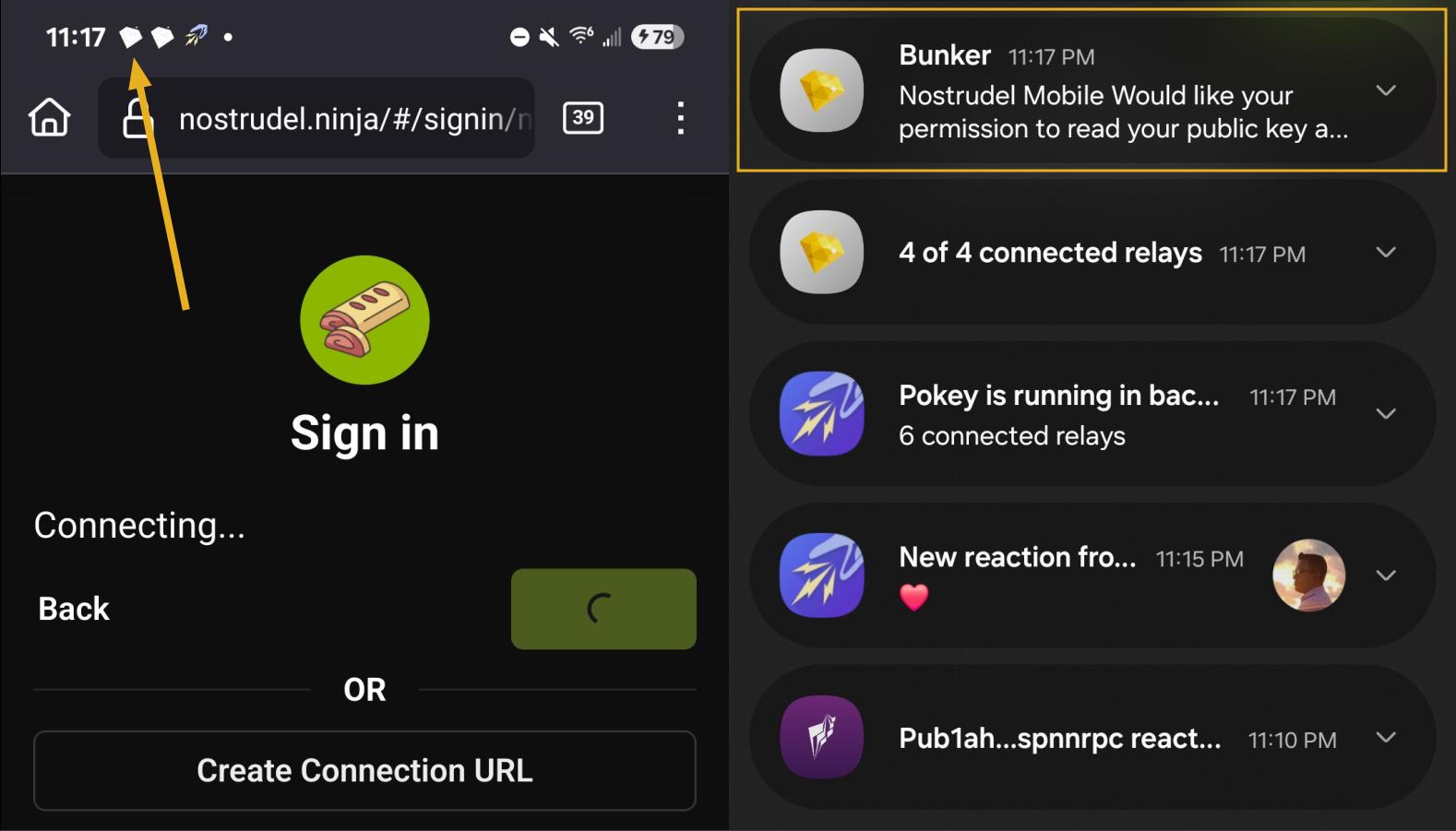 By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted. Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc. The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string. 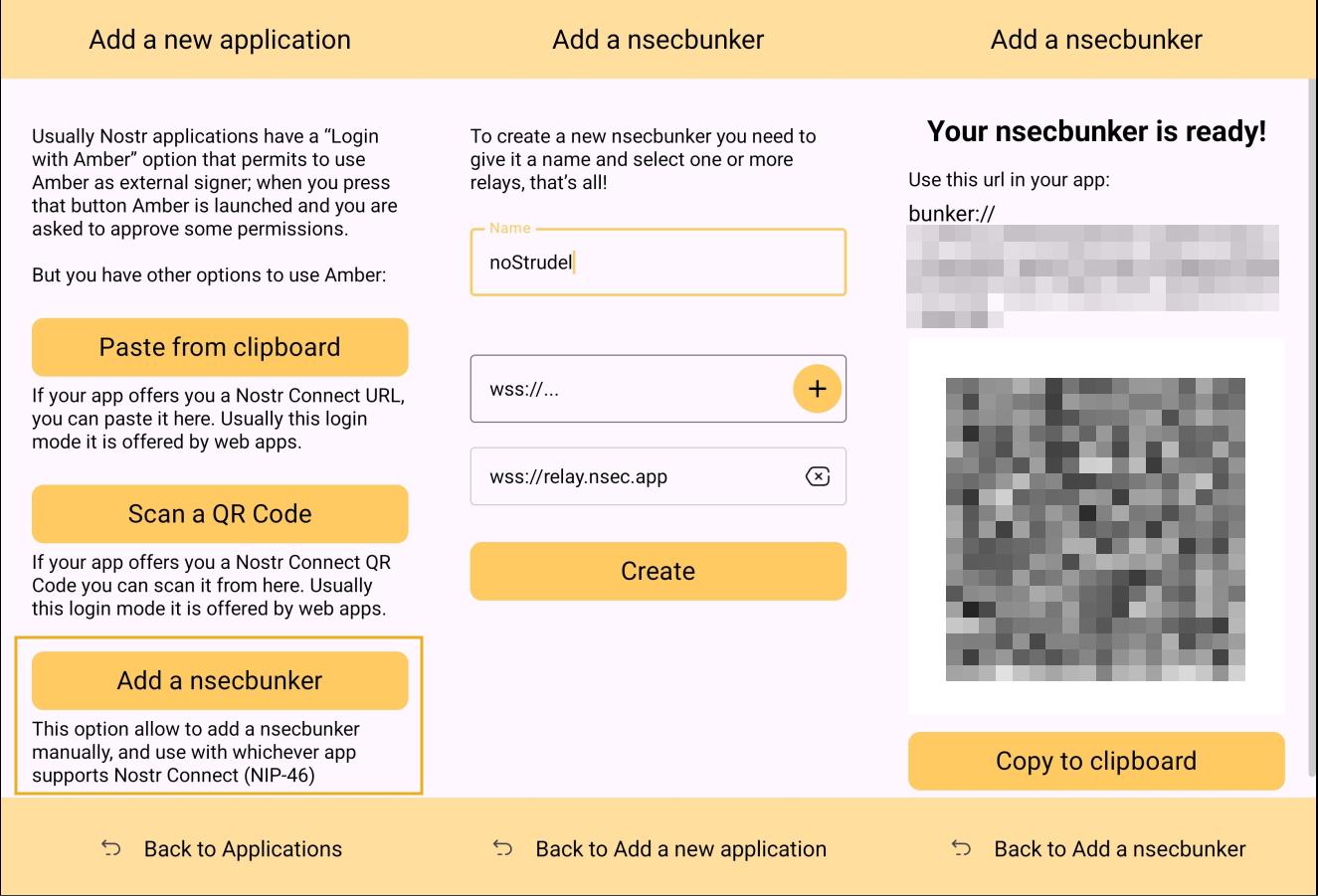 Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone. 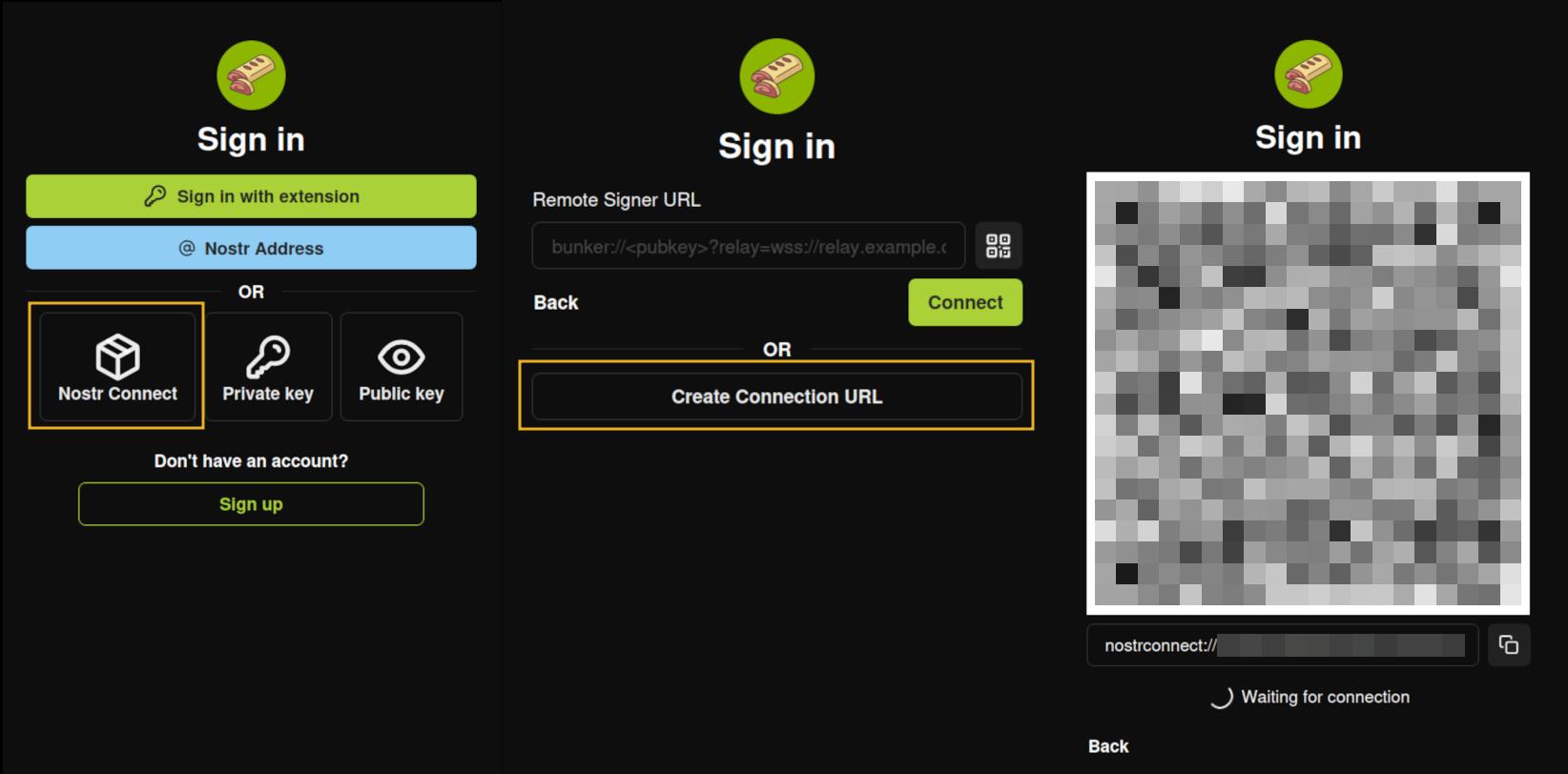 ### Multiple Accounts Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed. 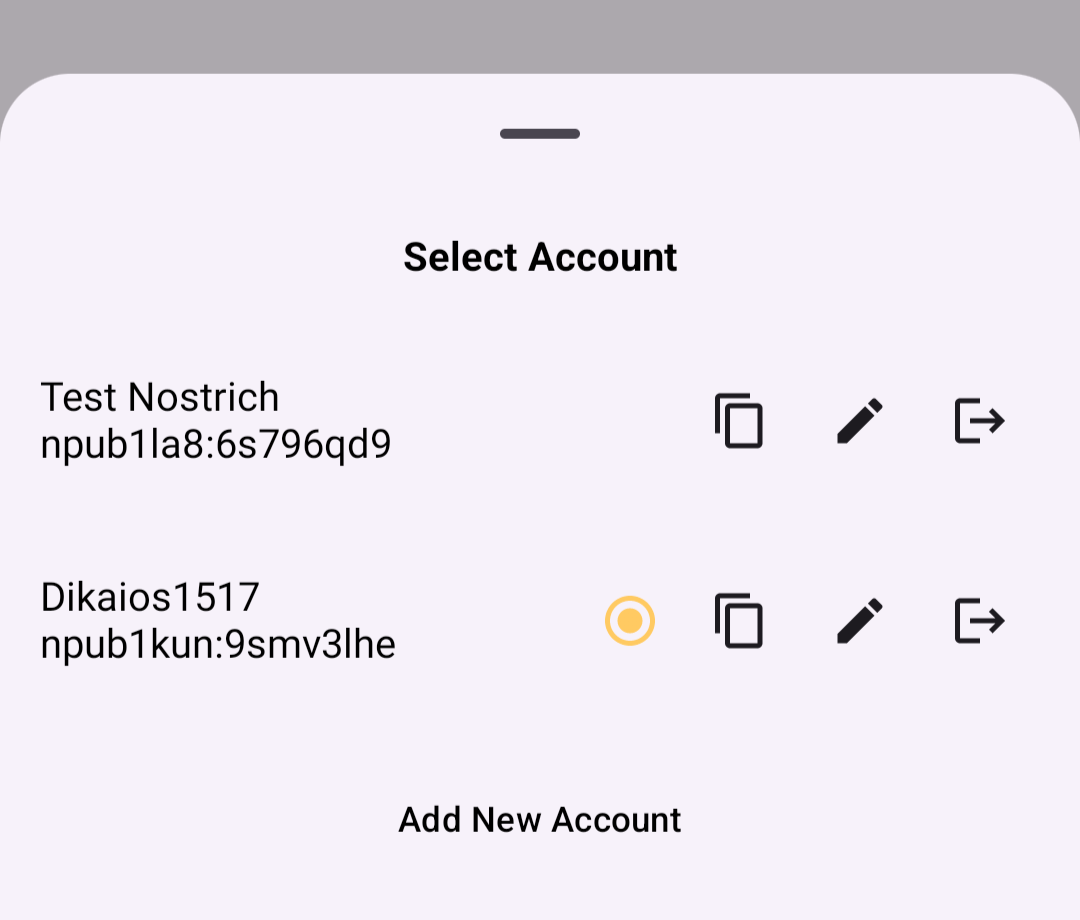 When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for. ### Key Backup & Restore Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec. 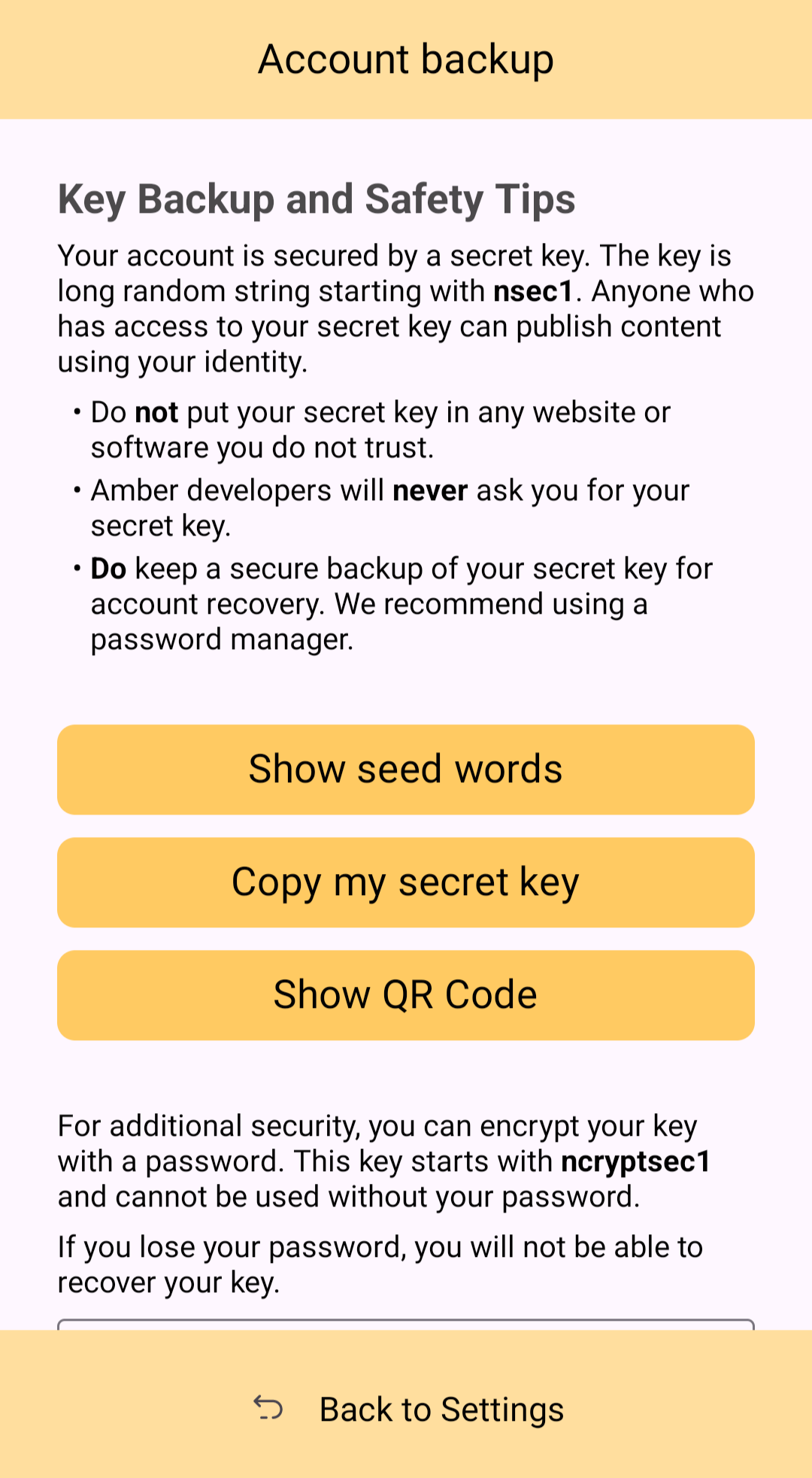 Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events. ### Tor Support While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity. 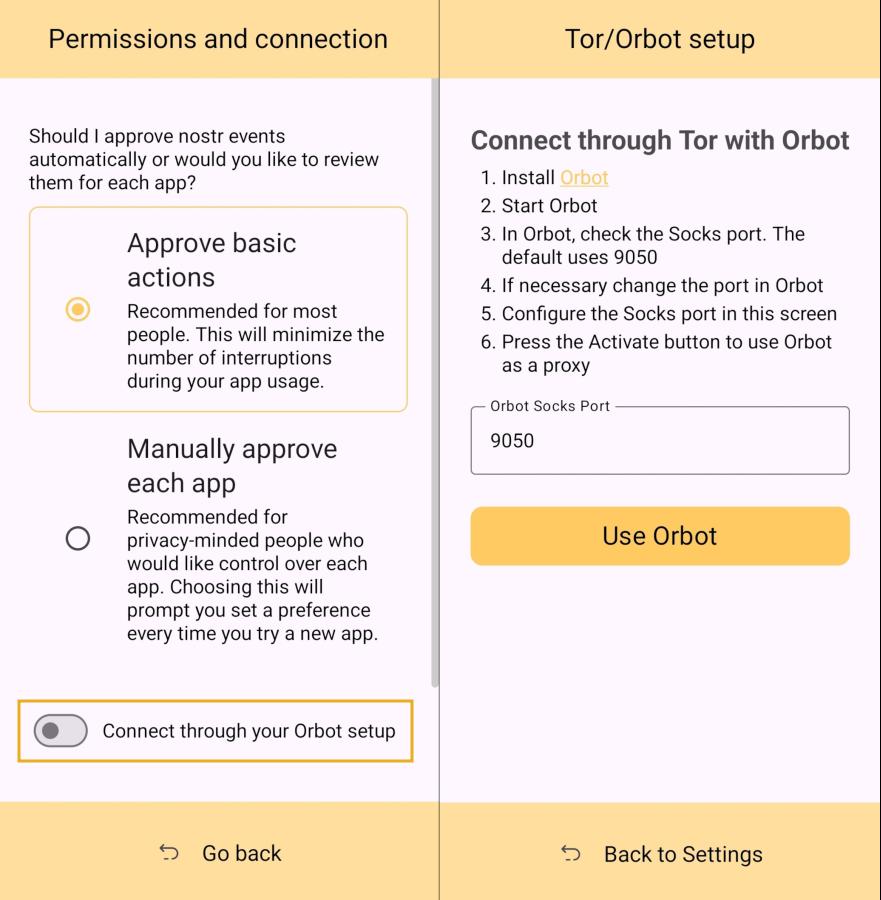 ### Additional Security Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access. ## Can My Grandma Use It? Score: **4.0** / 5 At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the ***same password*** for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs. That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touchpoint with Nostr, I think it holds up well, but could be somewhat streamlined. Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.  The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays. 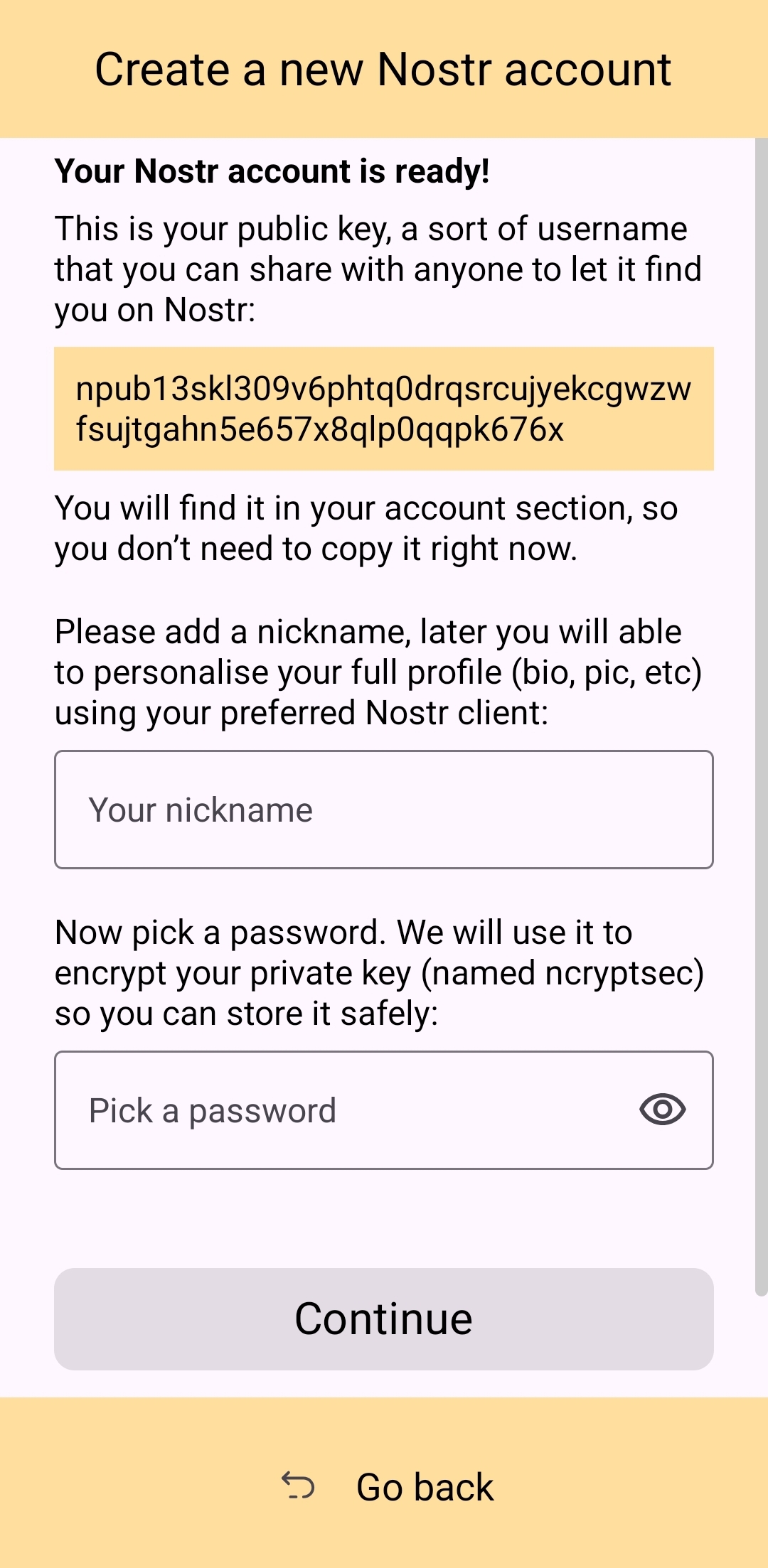 Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action. 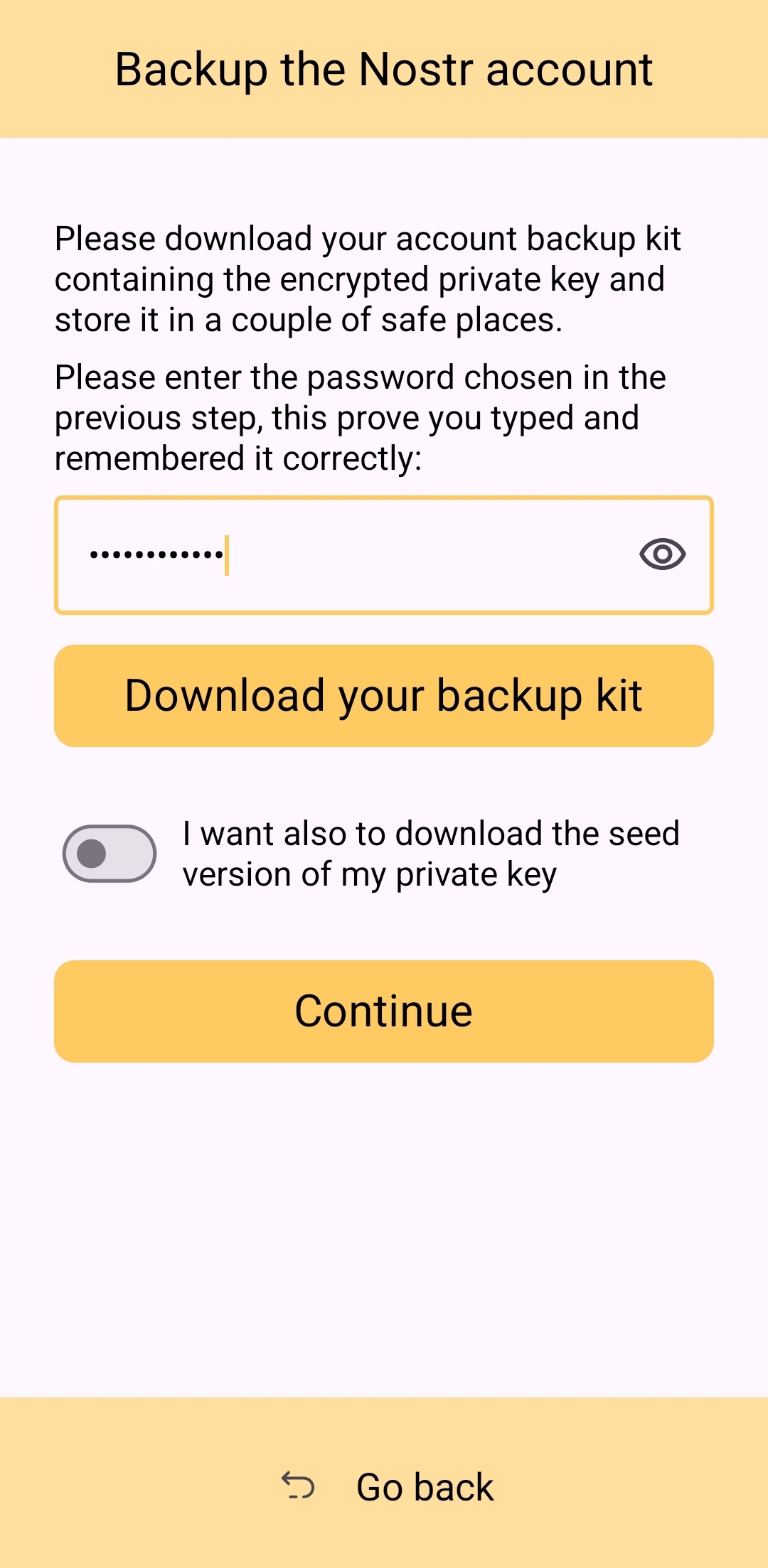 Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds. The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression. Now, I absolutely ***love*** the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process. Instead of: - Install Amber - Set up your keys - Install the client you want to use - Log in with Amber The process becomes: - Go to the Zapstore GitHub and download the latest version from the releases page. - Install the APK you downloaded, allowing any prompt to install unknown apps. - Open Zapstore and install Amber, allowing any prompt to install unknown apps again. - Open Amber and set up your keys. - Install the client you want to use - Log in with Amber An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store. ## How do UI Look? Score: **4.5** / 5 Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case. 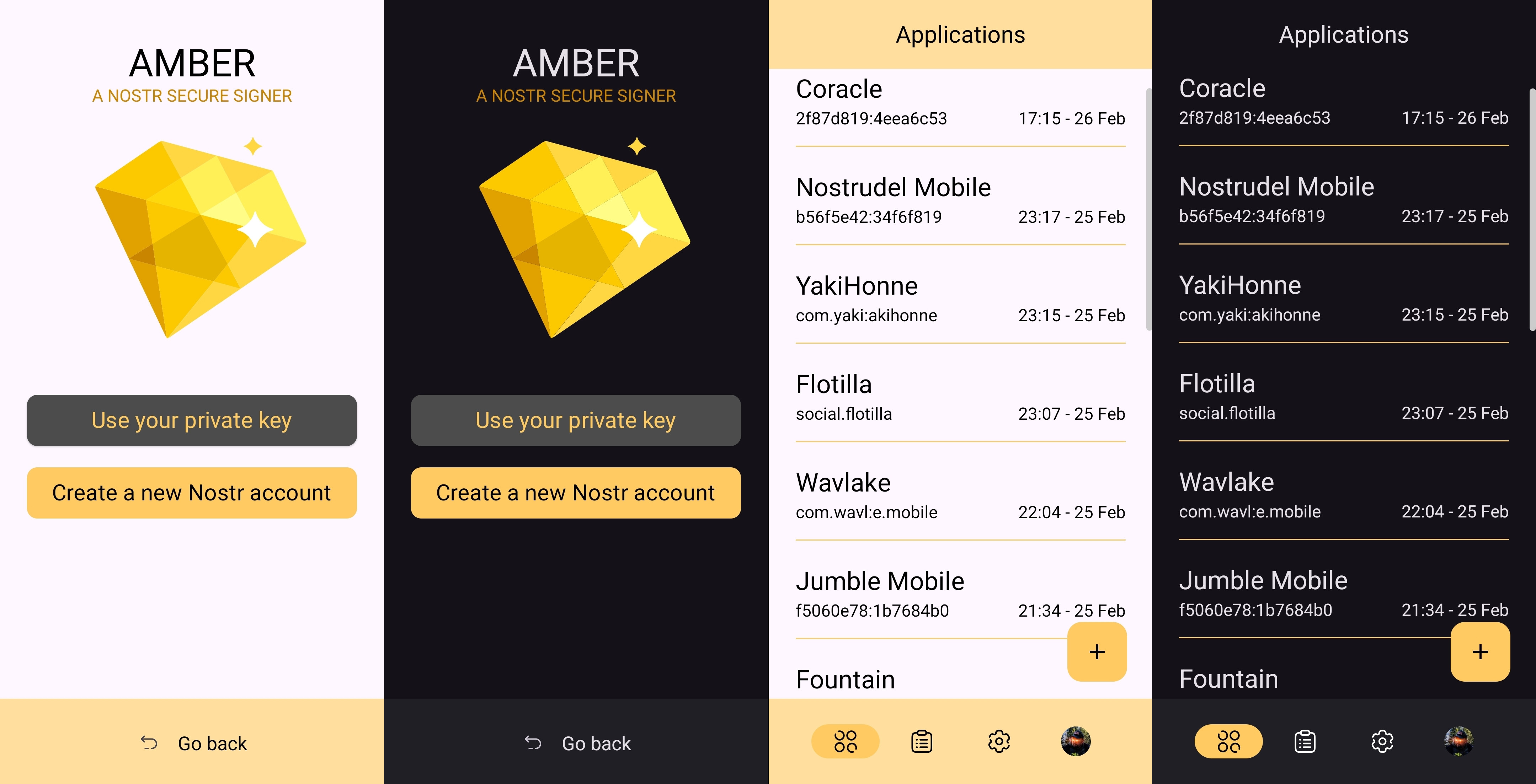 I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name. 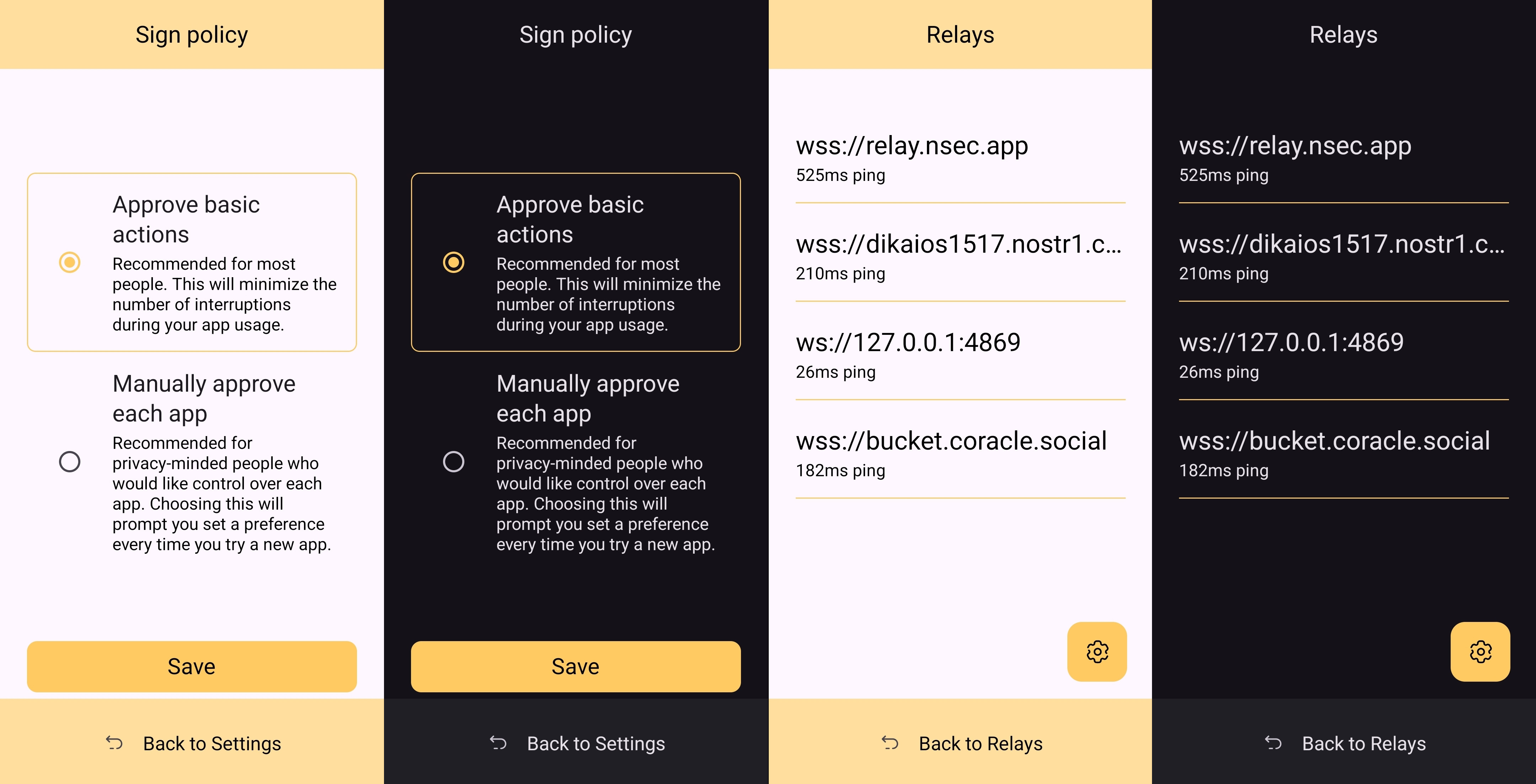 It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated. ## Relay Management Score: **4.9** / 5 Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture. In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings. 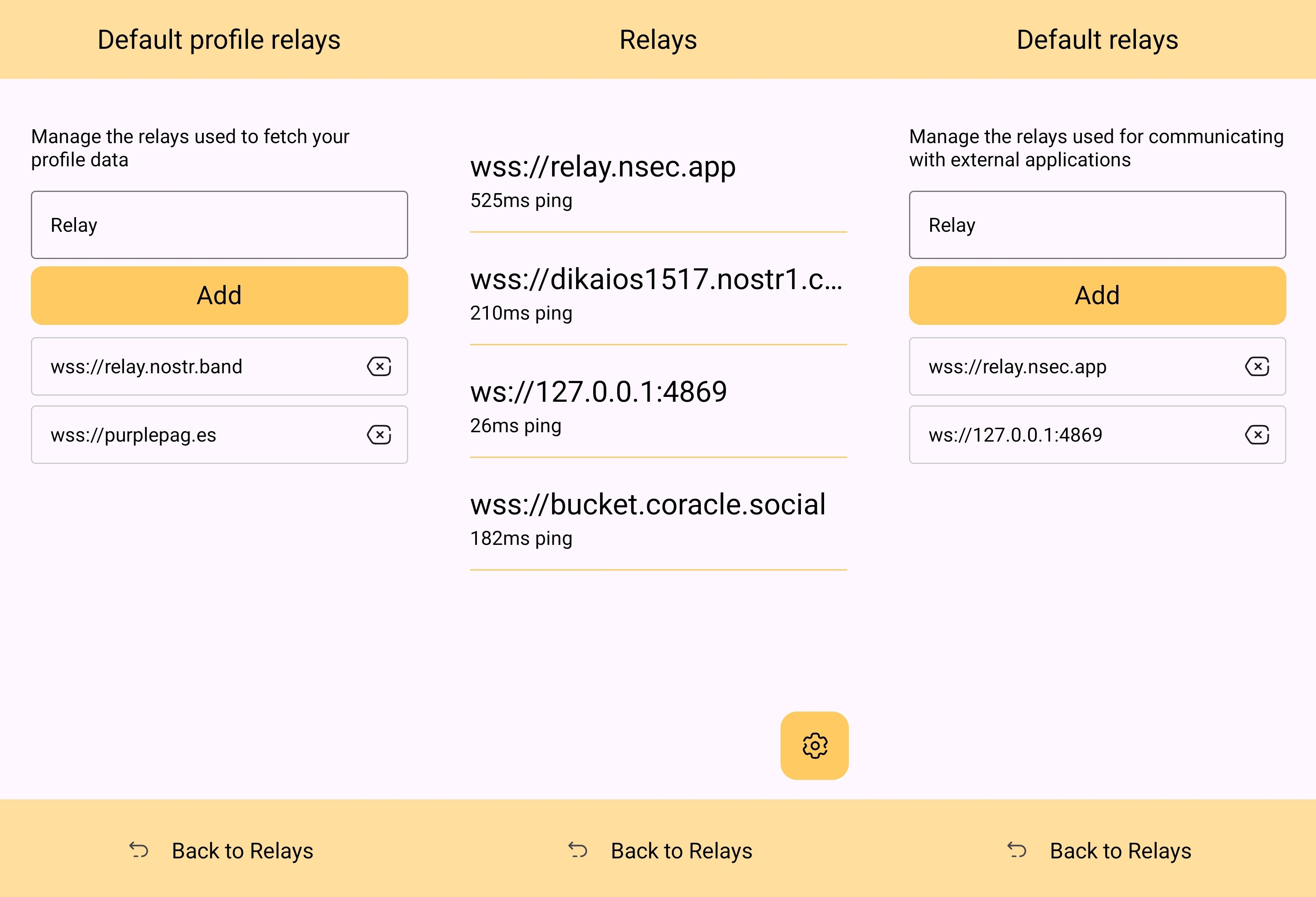 The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps. 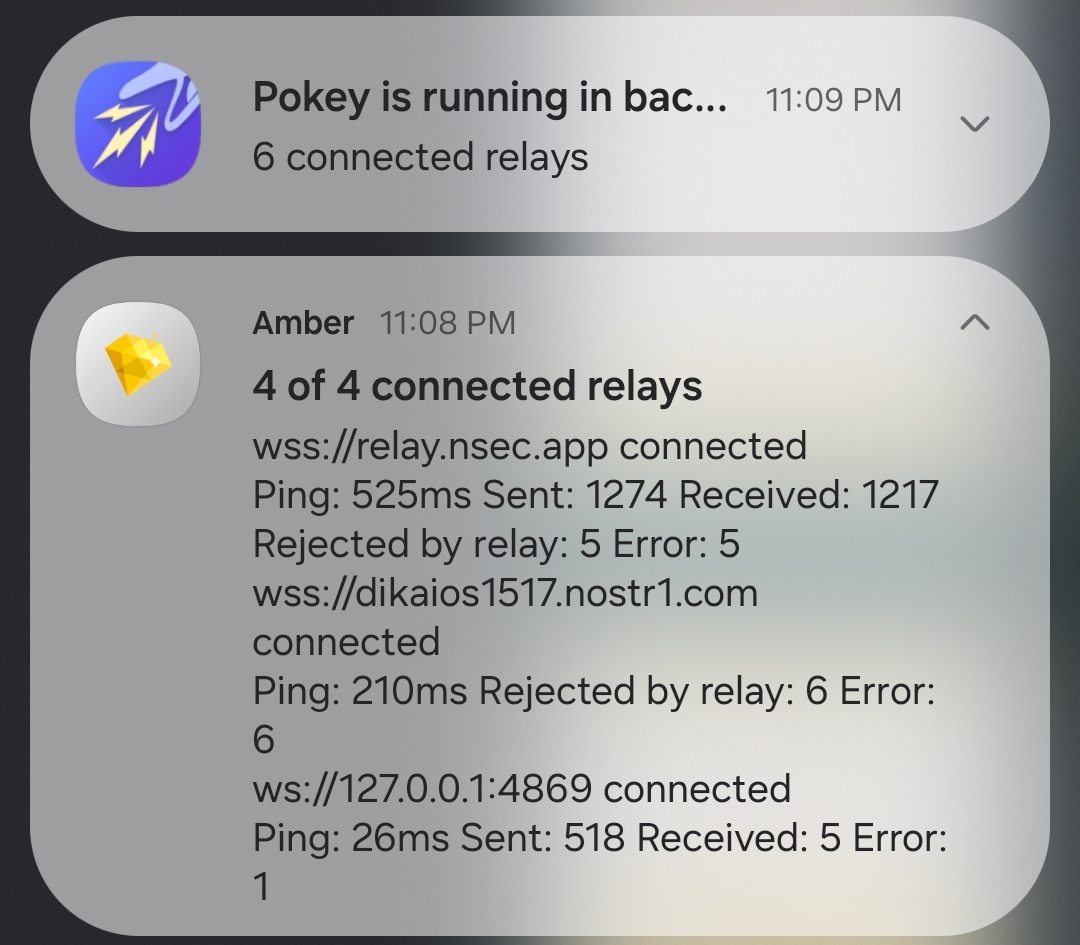 Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard. In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber. 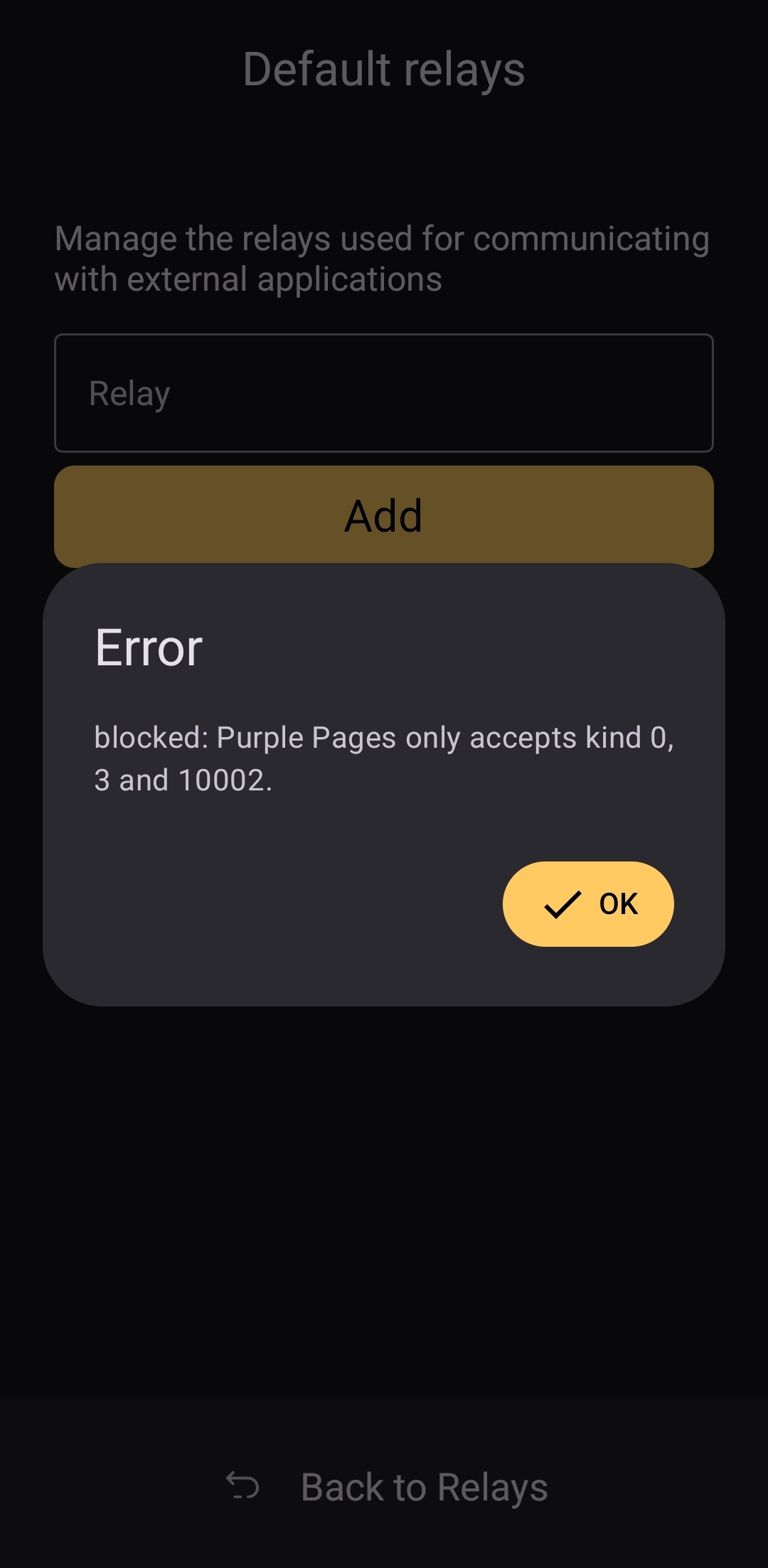 The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed. ## Current Users' Questions The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months. nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen. If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into. That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about ***how*** to use Amber, and that is a testament to Amber's ease of use all on its own. ## Wrap Up If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience. If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing. Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date! Now... What should I review next? @ b2d670de:907f9d4a
2025-02-28 16:39:38# onion-service-nostr-relays A list of nostr relays exposed as onion services. ## The list | Relay name | Description | Onion url | Operator | Payment URL | Payment options | | --- | --- | --- | --- | --- | --- | | nostr.oxtr.dev | Same relay as clearnet relay nostr.oxtr.dev | ws://oxtrdevav64z64yb7x6rjg4ntzqjhedm5b5zjqulugknhzr46ny2qbad.onion | [operator](nostr:nprofile1qqst94nsmefmya53crp5qq39kewrtgndqcynhnzp7j8lcu0qjple6jspz3mhxue69uhkummnw3ezummcw3ezuer9wcq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7jxrgyy) | N/A | N/A | | relay.snort.social | Same relay as clearnet relay relay.snort.social | wss://skzzn6cimfdv5e2phjc4yr5v7ikbxtn5f7dkwn5c7v47tduzlbosqmqd.onion | [operator](nostr:nprofile1qqsx8lnrrrw9skpulctgzruxm5y7rzlaw64tcf9qpqww9pt0xvzsfmgpzpmhxue69uhkummnw3ezuamfdejszxrhwden5te0wfjkccte9eekummjwsh8xmmrd9skct9tyup) | N/A | N/A | | nostr.thesamecat.io | Same relay as clearnet relay nostr.thesamecat.io | ws://2jsnlhfnelig5acq6iacydmzdbdmg7xwunm4xl6qwbvzacw4lwrjmlyd.onion | [operator](nostr:npub1wtuh24gpuxjyvnmjwlvxzg8k0elhasagfmmgz0x8vp4ltcy8ples54e7js) | N/A | N/A | | nostr.land | The nostr.land paid relay (same as clearnet) | ws://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion | [operator](nostr:npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj) | [Payment URL](http://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion) | BTC LN | | bitcoiner.social | No auth required, currently | ws://bitcoinr6de5lkvx4tpwdmzrdfdpla5sya2afwpcabjup2xpi5dulbad.onion | [operator](nostr:npub1an3nz7lczcunpdw6ltjst94hgzcxpppnk7zk3zr2nfcj4yd96kdse6twjd) | N/A | N/A | | relay.westernbtc.com | The westernbtc.com paid relay | ws://westbtcebhgi4ilxxziefho6bqu5lqwa5ncfjefnfebbhx2cwqx5knyd.onion | [operator](nostr:npub1pc57ls4rad5kvsp733suhzl2d4u9y7h4upt952a2pucnalc59teq33dmza) | [Payment URL](hjar34h5zwgtvxr345q7rncso3dhdaryuxgri3lu7lbhmnzvin72z5ad.onion) | BTC LN | | freelay.sovbit.host | Free relay for sovbit.host | ws://sovbitm2enxfr5ot6qscwy5ermdffbqscy66wirkbsigvcshumyzbbqd.onion | [operator](nostr:npub1gnwpctdec0aa00hfy4lvadftu08ccs9677mr73h9ddv2zvw8fu9smmerrq) | N/A | N/A | | nostr.sovbit.host | Paid relay for sovbit.host | ws://sovbitgz5uqyh7jwcsudq4sspxlj4kbnurvd3xarkkx2use3k6rlibqd.onion | [operator](nostr:npub1gnwpctdec0aa00hfy4lvadftu08ccs9677mr73h9ddv2zvw8fu9smmerrq) | N/A | N/A | | nostr.wine | 🍷 [nostr.wine](https://nostr.wine) relay | ws://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion) | BTC LN, BTC, Credit Card/CashApp (Stripe) | | inbox.nostr.wine | 🍷 [inbox.nostr.wine](https://inbox.nostr.wine) relay | ws://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion) | BTC LN, BTC | | filter.nostr.wine | 🍷 [filter.nostr.wine](https://filter.nostr.wine) proxy relay | ws://winefiltermhqixxzmnzxhrmaufpnfq3rmjcl6ei45iy4aidrngpsyid.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion/add-time) | BTC LN, BTC | | N/A | N/A | ws://pzfw4uteha62iwkzm3lycabk4pbtcr67cg5ymp5i3xwrpt3t24m6tzad.onion:81 | [operator](nostr:nprofile1q9z8wue69uhky6t5vdhkjmnjxejx2dtvddm8sdr5wpmkgmt6wfjxversd3sn2umevyexzenhwp3kzcn2w4cry7rsdy6kgatvvfskgtn0de5k7m30q9z8wue69uhk77r5wfjx2anpwcmrg73kx3ukydmcxeex5ee5de685ut2dpjkgmf4vg6h56n3w4k82emtde585u35xeh8jvn3vfskgtn0de5k7m30qqs93v545xjl0w8865rhw7kte0mkjxst88rk3k3xj53q4zdxm2zu5ectdn2z6) | N/A | N/A | | nostr.fractalized.net | Free relay for fractalized.net | ws://xvgox2zzo7cfxcjrd2llrkthvjs5t7efoalu34s6lmkqhvzvrms6ipyd.onion | [operator](nostr:npub1ky4kxtyg0uxgw8g5p5mmedh8c8s6sqny6zmaaqj44gv4rk0plaus3m4fd2) | N/A | N/A | | nfrelay.app | [nfrelay.app](https://nfrelay.app) aggregator relay (nostr-filter-relay) | ws://nfrelay6saohkmipikquvrn6d64dzxivhmcdcj4d5i7wxis47xwsriyd.onion | [operator](nostr:npub19dn7fq9hlxwjsdtgf28hyakcdmd73cccaf2u7a7vl42echey7ezs2hwja7) | N/A | N/A | relay.nostr.net | Public relay from nostr.net (Same as clearnet) | ws://nostrnetl6yd5whkldj3vqsxyyaq3tkuspy23a3qgx7cdepb4564qgqd.onion | [operator](https://nostr.at/aljaz@nostr.si) | N/A | N/A | | nerostrator | Free to read, pay XMR to relay | ws://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion | [operator](nostr:npub19j7zhftjfjnep4xa7zxhevschkqdvem9zr26dq4myhu6d62p3gqs3htnca) |[Payment URL](http://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion) | XMR | | nostr.girino.org | Public relay from nostr.girino.org | ws://gnostr2jnapk72mnagq3cuykfon73temzp77hcbncn4silgt77boruid.onion | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A | | wot.girino.org | WoT relay from wot.girino.org | ws://girwot2koy3kvj6fk7oseoqazp5vwbeawocb3m27jcqtah65f2fkl3yd.onion | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A | | haven.girino.org/{outbox, inbox, chat, private} | Haven smart relay from haven.girino.org | ws://ghaven2hi3qn2riitw7ymaztdpztrvmm337e2pgkacfh3rnscaoxjoad.onion/{outbox, inbox, chat, private} | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A | | relay.nostpy.lol | Free Web of Trust relay (Same as clearnet) | ws://pemgkkqjqjde7y2emc2hpxocexugbixp42o4zymznil6zfegx5nfp4id.onion | [operator](nostr:nprofile1qy08wumn8ghj7mn0wd68yttsw43zuam9d3kx7unyv4ezumn9wshszxrhwden5te0dehhxarj9enx6apwwa5h5tnzd9az7qpqg5pm4gf8hh7skp2rsnw9h2pvkr32sdnuhkcx9yte7qxmrg6v4txqr5amve) |N/A | N/A | | Poster.place Nostr Relay | N/A | ws://dmw5wbawyovz7fcahvguwkw4sknsqsalffwctioeoqkvvy7ygjbcuoad.onion | [operator](nostr:nprofile1qqsr836yylem9deatcu08ekfj8qj9f2aypq8ydt0w8dyng8zp8akjsqpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0ds6xxx6y) | N/A | N/A | | Azzamo Relay | [Azzamo](https://azzamo.net/relays/) Premium Nostr relay. (paid) | ws://q6a7m5qkyonzb5fk5yv4jyu3ar44hqedn7wjopg737lit2ckkhx2nyid.onion | [operator](nostr:npub1jjn20zj6awa6gz73423zxjqszvkzmqqyhwghwctvgy7ncrwlxg8qdavknm) | [Payment URL](https://azzamo.net/pay) | BTC LN | | Azzamo Inbox Relay | [Azzamo](https://azzamo.net/inbox-relay/) Group and Private message relay. (Freemium) | ws://gp5kiwqfw7t2fwb3rfts2aekoph4x7pj5pv65re2y6hzaujsxewanbqd.onion | [operator](nostr:npub1jjn20zj6awa6gz73423zxjqszvkzmqqyhwghwctvgy7ncrwlxg8qdavknm) | [Payment URL](https://azzamo.net/pay) | BTC LN | | Noderunners Relay | The official [Noderunners](https://noderunners.network) Nostr Relay. | ws://35vr3xigzjv2xyzfyif6o2gksmkioppy4rmwag7d4bqmwuccs2u4jaid.onion | [operator](nostr:nprofile1qqsqarzpaw2xv4cc36n092krdsj78yll7n2pfx5rv7fzp4n9jhlsl2spz3mhxue69uhhwmm59esh57npd4hjumn9wsq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tqd6ns) | [Payment URL](https://noderunners.azzamo.net) | BTC LN | ## Contributing Contributions are encouraged to keep this document alive. Just open a PR and I'll have it tested and merged. The onion URL is the only mandatory column, the rest is just nice-to-have metadata about the relay. Put `N/A` in empty columns. If you want to contribute anonymously, please contact me on [SimpleX](https://simplex.chat/contact#/?v=2&smp=smp%3A%2F%2F0YuTwO05YJWS8rkjn9eLJDjQhFKvIYd8d4xG8X1blIU%3D%40smp8.simplex.im%2FZ_4q0Nv91wCk8Uekyiaas7NSr-nEDir7%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAvdSLn5QEwrfKQswQGTzlwtXeLMXbzxErv-zOJU6D0y8%253D%26srv%3Dbeccx4yfxxbvyhqypaavemqurytl6hozr47wfc7uuecacjqdvwpw2xid.onion) or send a DM on nostr using a disposable npub. ### Operator column It is generally preferred to use something that includes a NIP-19 string, either just the string or a url that contains the NIP-19 string in it (e.g. an njump url).
@ b2d670de:907f9d4a
2025-02-28 16:39:38# onion-service-nostr-relays A list of nostr relays exposed as onion services. ## The list | Relay name | Description | Onion url | Operator | Payment URL | Payment options | | --- | --- | --- | --- | --- | --- | | nostr.oxtr.dev | Same relay as clearnet relay nostr.oxtr.dev | ws://oxtrdevav64z64yb7x6rjg4ntzqjhedm5b5zjqulugknhzr46ny2qbad.onion | [operator](nostr:nprofile1qqst94nsmefmya53crp5qq39kewrtgndqcynhnzp7j8lcu0qjple6jspz3mhxue69uhkummnw3ezummcw3ezuer9wcq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7jxrgyy) | N/A | N/A | | relay.snort.social | Same relay as clearnet relay relay.snort.social | wss://skzzn6cimfdv5e2phjc4yr5v7ikbxtn5f7dkwn5c7v47tduzlbosqmqd.onion | [operator](nostr:nprofile1qqsx8lnrrrw9skpulctgzruxm5y7rzlaw64tcf9qpqww9pt0xvzsfmgpzpmhxue69uhkummnw3ezuamfdejszxrhwden5te0wfjkccte9eekummjwsh8xmmrd9skct9tyup) | N/A | N/A | | nostr.thesamecat.io | Same relay as clearnet relay nostr.thesamecat.io | ws://2jsnlhfnelig5acq6iacydmzdbdmg7xwunm4xl6qwbvzacw4lwrjmlyd.onion | [operator](nostr:npub1wtuh24gpuxjyvnmjwlvxzg8k0elhasagfmmgz0x8vp4ltcy8ples54e7js) | N/A | N/A | | nostr.land | The nostr.land paid relay (same as clearnet) | ws://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion | [operator](nostr:npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj) | [Payment URL](http://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion) | BTC LN | | bitcoiner.social | No auth required, currently | ws://bitcoinr6de5lkvx4tpwdmzrdfdpla5sya2afwpcabjup2xpi5dulbad.onion | [operator](nostr:npub1an3nz7lczcunpdw6ltjst94hgzcxpppnk7zk3zr2nfcj4yd96kdse6twjd) | N/A | N/A | | relay.westernbtc.com | The westernbtc.com paid relay | ws://westbtcebhgi4ilxxziefho6bqu5lqwa5ncfjefnfebbhx2cwqx5knyd.onion | [operator](nostr:npub1pc57ls4rad5kvsp733suhzl2d4u9y7h4upt952a2pucnalc59teq33dmza) | [Payment URL](hjar34h5zwgtvxr345q7rncso3dhdaryuxgri3lu7lbhmnzvin72z5ad.onion) | BTC LN | | freelay.sovbit.host | Free relay for sovbit.host | ws://sovbitm2enxfr5ot6qscwy5ermdffbqscy66wirkbsigvcshumyzbbqd.onion | [operator](nostr:npub1gnwpctdec0aa00hfy4lvadftu08ccs9677mr73h9ddv2zvw8fu9smmerrq) | N/A | N/A | | nostr.sovbit.host | Paid relay for sovbit.host | ws://sovbitgz5uqyh7jwcsudq4sspxlj4kbnurvd3xarkkx2use3k6rlibqd.onion | [operator](nostr:npub1gnwpctdec0aa00hfy4lvadftu08ccs9677mr73h9ddv2zvw8fu9smmerrq) | N/A | N/A | | nostr.wine | 🍷 [nostr.wine](https://nostr.wine) relay | ws://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion) | BTC LN, BTC, Credit Card/CashApp (Stripe) | | inbox.nostr.wine | 🍷 [inbox.nostr.wine](https://inbox.nostr.wine) relay | ws://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion) | BTC LN, BTC | | filter.nostr.wine | 🍷 [filter.nostr.wine](https://filter.nostr.wine) proxy relay | ws://winefiltermhqixxzmnzxhrmaufpnfq3rmjcl6ei45iy4aidrngpsyid.onion | [operator](nostr:npub1fyvwkve2gxm3h2d8fvwuvsnkell4jtj4zpae8w4w8zhn2g89t96s0tsfuk) | [Payment URL](http://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion/add-time) | BTC LN, BTC | | N/A | N/A | ws://pzfw4uteha62iwkzm3lycabk4pbtcr67cg5ymp5i3xwrpt3t24m6tzad.onion:81 | [operator](nostr:nprofile1q9z8wue69uhky6t5vdhkjmnjxejx2dtvddm8sdr5wpmkgmt6wfjxversd3sn2umevyexzenhwp3kzcn2w4cry7rsdy6kgatvvfskgtn0de5k7m30q9z8wue69uhk77r5wfjx2anpwcmrg73kx3ukydmcxeex5ee5de685ut2dpjkgmf4vg6h56n3w4k82emtde585u35xeh8jvn3vfskgtn0de5k7m30qqs93v545xjl0w8865rhw7kte0mkjxst88rk3k3xj53q4zdxm2zu5ectdn2z6) | N/A | N/A | | nostr.fractalized.net | Free relay for fractalized.net | ws://xvgox2zzo7cfxcjrd2llrkthvjs5t7efoalu34s6lmkqhvzvrms6ipyd.onion | [operator](nostr:npub1ky4kxtyg0uxgw8g5p5mmedh8c8s6sqny6zmaaqj44gv4rk0plaus3m4fd2) | N/A | N/A | | nfrelay.app | [nfrelay.app](https://nfrelay.app) aggregator relay (nostr-filter-relay) | ws://nfrelay6saohkmipikquvrn6d64dzxivhmcdcj4d5i7wxis47xwsriyd.onion | [operator](nostr:npub19dn7fq9hlxwjsdtgf28hyakcdmd73cccaf2u7a7vl42echey7ezs2hwja7) | N/A | N/A | relay.nostr.net | Public relay from nostr.net (Same as clearnet) | ws://nostrnetl6yd5whkldj3vqsxyyaq3tkuspy23a3qgx7cdepb4564qgqd.onion | [operator](https://nostr.at/aljaz@nostr.si) | N/A | N/A | | nerostrator | Free to read, pay XMR to relay | ws://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion | [operator](nostr:npub19j7zhftjfjnep4xa7zxhevschkqdvem9zr26dq4myhu6d62p3gqs3htnca) |[Payment URL](http://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion) | XMR | | nostr.girino.org | Public relay from nostr.girino.org | ws://gnostr2jnapk72mnagq3cuykfon73temzp77hcbncn4silgt77boruid.onion | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A | | wot.girino.org | WoT relay from wot.girino.org | ws://girwot2koy3kvj6fk7oseoqazp5vwbeawocb3m27jcqtah65f2fkl3yd.onion | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A | | haven.girino.org/{outbox, inbox, chat, private} | Haven smart relay from haven.girino.org | ws://ghaven2hi3qn2riitw7ymaztdpztrvmm337e2pgkacfh3rnscaoxjoad.onion/{outbox, inbox, chat, private} | [operator](nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz) | N/A | N/A | | relay.nostpy.lol | Free Web of Trust relay (Same as clearnet) | ws://pemgkkqjqjde7y2emc2hpxocexugbixp42o4zymznil6zfegx5nfp4id.onion | [operator](nostr:nprofile1qy08wumn8ghj7mn0wd68yttsw43zuam9d3kx7unyv4ezumn9wshszxrhwden5te0dehhxarj9enx6apwwa5h5tnzd9az7qpqg5pm4gf8hh7skp2rsnw9h2pvkr32sdnuhkcx9yte7qxmrg6v4txqr5amve) |N/A | N/A | | Poster.place Nostr Relay | N/A | ws://dmw5wbawyovz7fcahvguwkw4sknsqsalffwctioeoqkvvy7ygjbcuoad.onion | [operator](nostr:nprofile1qqsr836yylem9deatcu08ekfj8qj9f2aypq8ydt0w8dyng8zp8akjsqpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0ds6xxx6y) | N/A | N/A | | Azzamo Relay | [Azzamo](https://azzamo.net/relays/) Premium Nostr relay. (paid) | ws://q6a7m5qkyonzb5fk5yv4jyu3ar44hqedn7wjopg737lit2ckkhx2nyid.onion | [operator](nostr:npub1jjn20zj6awa6gz73423zxjqszvkzmqqyhwghwctvgy7ncrwlxg8qdavknm) | [Payment URL](https://azzamo.net/pay) | BTC LN | | Azzamo Inbox Relay | [Azzamo](https://azzamo.net/inbox-relay/) Group and Private message relay. (Freemium) | ws://gp5kiwqfw7t2fwb3rfts2aekoph4x7pj5pv65re2y6hzaujsxewanbqd.onion | [operator](nostr:npub1jjn20zj6awa6gz73423zxjqszvkzmqqyhwghwctvgy7ncrwlxg8qdavknm) | [Payment URL](https://azzamo.net/pay) | BTC LN | | Noderunners Relay | The official [Noderunners](https://noderunners.network) Nostr Relay. | ws://35vr3xigzjv2xyzfyif6o2gksmkioppy4rmwag7d4bqmwuccs2u4jaid.onion | [operator](nostr:nprofile1qqsqarzpaw2xv4cc36n092krdsj78yll7n2pfx5rv7fzp4n9jhlsl2spz3mhxue69uhhwmm59esh57npd4hjumn9wsq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tqd6ns) | [Payment URL](https://noderunners.azzamo.net) | BTC LN | ## Contributing Contributions are encouraged to keep this document alive. Just open a PR and I'll have it tested and merged. The onion URL is the only mandatory column, the rest is just nice-to-have metadata about the relay. Put `N/A` in empty columns. If you want to contribute anonymously, please contact me on [SimpleX](https://simplex.chat/contact#/?v=2&smp=smp%3A%2F%2F0YuTwO05YJWS8rkjn9eLJDjQhFKvIYd8d4xG8X1blIU%3D%40smp8.simplex.im%2FZ_4q0Nv91wCk8Uekyiaas7NSr-nEDir7%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAvdSLn5QEwrfKQswQGTzlwtXeLMXbzxErv-zOJU6D0y8%253D%26srv%3Dbeccx4yfxxbvyhqypaavemqurytl6hozr47wfc7uuecacjqdvwpw2xid.onion) or send a DM on nostr using a disposable npub. ### Operator column It is generally preferred to use something that includes a NIP-19 string, either just the string or a url that contains the NIP-19 string in it (e.g. an njump url). @ b2d670de:907f9d4a
2025-02-26 18:27:47This is a list of nostr clients exposed as onion services. The list is currently actively maintained on [GitHub](https://github.com/0xtrr/onion-service-nostr-clients). Contributions are always appreciated! | Client name | Onion URL | Source code URL | Admin | Description | | --- | --- | --- | --- | --- | | Snort | http://agzj5a4be3kgp6yurijk4q7pm2yh4a5nphdg4zozk365yirf7ahuctyd.onion | https://git.v0l.io/Kieran/snort | [operator](nostr:nprofile1qyvhwumn8ghj7un9d3shjtnndehhyapwwdhkx6tpdshszxnhwden5te0wpuhyctdd9jzuenfv96x5ctx9e3k7mf0qqsx8lnrrrw9skpulctgzruxm5y7rzlaw64tcf9qpqww9pt0xvzsfmg9umdvr) | N/A | | moStard | http://sifbugd5nwdq77plmidkug4y57zuqwqio3zlyreizrhejhp6bohfwkad.onion/ | https://github.com/rafael-xmr/nostrudel/tree/mostard | [operator](nostr:nprofile1qyv8wumn8ghj7un9d3shjtnddaehgctjvshx7un89uq36amnwvaz7tmzdaehgu3wvf5hgcm0d9h8g7r0ddhjucm0d5hsqgy8wvyzw6l9pn5m47n7tcm5un7t7h5ctx3pjx8nfwh06qq8g6max5zadtyx) | minimalist monero friendly nostrudel fork | | Nostrudel | http://oxtrnmb4wsb77rmk64q3jfr55fo33luwmsyaoovicyhzgrulleiojsad.onion/ | https://github.com/hzrd149/nostrudel | [operator](nostrnpub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0) | Runs latest tagged docker image | | Nostrudel Next | http://oxtrnnumsflm7hmvb3xqphed2eqpbrt4seflgmdsjnpgc3ejd6iycuyd.onion/ | https://github.com/hzrd149/nostrudel | [operator](nostr:npub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0) | Runs latest "next" tagged docker image | | Nsite | http://q457mvdt5smqj726m4lsqxxdyx7r3v7gufzt46zbkop6mkghpnr7z3qd.onion/ | https://github.com/hzrd149/nsite-ts | [operator](nostr:nprofile1qqszv6q4uryjzr06xfxxew34wwc5hmjfmfpqn229d72gfegsdn2q3fgpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0dsxx2q3a) | Runs nsite. You can read more about nsite [here](https://github.com/lez/nsite). | | Shopstr | http://6fkdn756yryd5wurkq7ifnexupnfwj6sotbtby2xhj5baythl4cyf2id.onion/ | https://github.com/shopstr-eng/shopstr-hidden-service | [operator](nostr:nprofile1qqsdxm5qs0a8kdk6aejxew9nlx074g7cnedrjeggws0sq03p4s9khmqpz9mhxue69uhkummnw3ezuamfdejj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhksctkv4hzucmpd3mxztnyv4mz747p6g5) | Runs the latest `serverless` branch build of Shopstr. |
@ b2d670de:907f9d4a
2025-02-26 18:27:47This is a list of nostr clients exposed as onion services. The list is currently actively maintained on [GitHub](https://github.com/0xtrr/onion-service-nostr-clients). Contributions are always appreciated! | Client name | Onion URL | Source code URL | Admin | Description | | --- | --- | --- | --- | --- | | Snort | http://agzj5a4be3kgp6yurijk4q7pm2yh4a5nphdg4zozk365yirf7ahuctyd.onion | https://git.v0l.io/Kieran/snort | [operator](nostr:nprofile1qyvhwumn8ghj7un9d3shjtnndehhyapwwdhkx6tpdshszxnhwden5te0wpuhyctdd9jzuenfv96x5ctx9e3k7mf0qqsx8lnrrrw9skpulctgzruxm5y7rzlaw64tcf9qpqww9pt0xvzsfmg9umdvr) | N/A | | moStard | http://sifbugd5nwdq77plmidkug4y57zuqwqio3zlyreizrhejhp6bohfwkad.onion/ | https://github.com/rafael-xmr/nostrudel/tree/mostard | [operator](nostr:nprofile1qyv8wumn8ghj7un9d3shjtnddaehgctjvshx7un89uq36amnwvaz7tmzdaehgu3wvf5hgcm0d9h8g7r0ddhjucm0d5hsqgy8wvyzw6l9pn5m47n7tcm5un7t7h5ctx3pjx8nfwh06qq8g6max5zadtyx) | minimalist monero friendly nostrudel fork | | Nostrudel | http://oxtrnmb4wsb77rmk64q3jfr55fo33luwmsyaoovicyhzgrulleiojsad.onion/ | https://github.com/hzrd149/nostrudel | [operator](nostrnpub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0) | Runs latest tagged docker image | | Nostrudel Next | http://oxtrnnumsflm7hmvb3xqphed2eqpbrt4seflgmdsjnpgc3ejd6iycuyd.onion/ | https://github.com/hzrd149/nostrudel | [operator](nostr:npub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0) | Runs latest "next" tagged docker image | | Nsite | http://q457mvdt5smqj726m4lsqxxdyx7r3v7gufzt46zbkop6mkghpnr7z3qd.onion/ | https://github.com/hzrd149/nsite-ts | [operator](nostr:nprofile1qqszv6q4uryjzr06xfxxew34wwc5hmjfmfpqn229d72gfegsdn2q3fgpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0dsxx2q3a) | Runs nsite. You can read more about nsite [here](https://github.com/lez/nsite). | | Shopstr | http://6fkdn756yryd5wurkq7ifnexupnfwj6sotbtby2xhj5baythl4cyf2id.onion/ | https://github.com/shopstr-eng/shopstr-hidden-service | [operator](nostr:nprofile1qqsdxm5qs0a8kdk6aejxew9nlx074g7cnedrjeggws0sq03p4s9khmqpz9mhxue69uhkummnw3ezuamfdejj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhksctkv4hzucmpd3mxztnyv4mz747p6g5) | Runs the latest `serverless` branch build of Shopstr. | @ 4857600b:30b502f4
2025-02-20 19:09:11Mitch McConnell, a senior Republican senator, announced he will not seek reelection. At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering. McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era.
@ 4857600b:30b502f4
2025-02-20 19:09:11Mitch McConnell, a senior Republican senator, announced he will not seek reelection. At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering. McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era. @ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables **decentralized, censorship-resistant communication**. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on **users, developers, and relay operators**. If you believe in **free speech, decentralization, and an open internet**, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, **every effort helps build a more robust network**. Here’s how you can get involved and make a difference. --- ## **1️⃣ Use Nostr Daily** The simplest and most effective way to contribute to Nostr is by **using it regularly**. The more active users, the stronger and more valuable the network becomes. ✅ **Post, comment, and zap** (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ **Engage with new users** and help them understand how Nostr works.\ ✅ **Try different Nostr clients** like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience. Your activity **keeps the network alive** and helps encourage more developers and relay operators to invest in the ecosystem. --- ## **2️⃣ Run Your Own Nostr Relay** Relays are the **backbone of Nostr**, responsible for distributing messages across the network. The more **independent relays exist**, the stronger and more censorship-resistant Nostr becomes. ✅ **Set up your own relay** to help decentralize the network further.\ ✅ **Experiment with relay configurations** and different performance optimizations.\ ✅ **Offer public or private relay services** to users looking for high-quality infrastructure. If you're not technical, you can still **support relay operators** by **subscribing to a paid relay** or donating to open-source relay projects. --- ## **3️⃣ Support Paid Relays & Infrastructure** Free relays have helped Nostr grow, but they **struggle with spam, slow speeds, and sustainability issues**. **Paid relays** help fund **better infrastructure, faster message delivery, and a more reliable experience**. ✅ **Subscribe to a paid relay** to help keep it running.\ ✅ **Use premium services** like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ **Donate to relay operators** who invest in long-term infrastructure. By funding **Nostr’s decentralized backbone**, you help ensure its **longevity and reliability**. --- ## **4️⃣ Zap Developers, Creators & Builders** Many people contribute to Nostr **without direct financial compensation**—developers who build clients, relay operators, educators, and content creators. **You can support them with zaps!** ⚡ ✅ **Find developers working on Nostr projects** and send them a zap.\ ✅ **Support content creators and educators** who spread awareness about Nostr.\ ✅ **Encourage builders** by donating to open-source projects. Micro-payments via the **Lightning Network** make it easy to directly **support the people who make Nostr better**. --- ## **5️⃣ Develop New Nostr Apps & Tools** If you're a developer, you can **build on Nostr’s open protocol** to create new apps, bots, or tools. Nostr is **permissionless**, meaning anyone can develop for it. ✅ **Create new Nostr clients** with unique features and user experiences.\ ✅ **Build bots or automation tools** that improve engagement and usability.\ ✅ **Experiment with decentralized identity, authentication, and encryption** to make Nostr even stronger. With **no corporate gatekeepers**, your projects can help shape the future of decentralized social media. --- ## **6️⃣ Promote & Educate Others About Nostr** Adoption grows when **more people understand and use Nostr**. You can help by **spreading awareness** and creating educational content. ✅ **Write blogs, guides, and tutorials** explaining how to use Nostr.\ ✅ **Make videos or social media posts** introducing new users to the protocol.\ ✅ **Host discussions, Twitter Spaces, or workshops** to onboard more people. The more people **understand and trust Nostr**, the stronger the ecosystem becomes. --- ## **7️⃣ Support Open-Source Nostr Projects** Many Nostr tools and clients are **built by volunteers**, and open-source projects thrive on **community support**. ✅ **Contribute code** to existing Nostr projects on GitHub.\ ✅ **Report bugs and suggest features** to improve Nostr clients.\ ✅ **Donate to developers** who keep Nostr free and open for everyone. If you're not a developer, you can still **help with testing, translations, and documentation** to make projects more accessible. --- ## **🚀 Every Contribution Strengthens Nostr** Whether you: ✔️ **Post and engage daily**\ ✔️ **Zap creators and developers**\ ✔️ **Run or support relays**\ ✔️ **Build new apps and tools**\ ✔️ **Educate and onboard new users** **Every action helps make Nostr more resilient, decentralized, and unstoppable.** Nostr isn’t just another social network—it’s **a movement toward a free and open internet**. If you believe in **digital freedom, privacy, and decentralization**, now is the time to get involved.
@ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables **decentralized, censorship-resistant communication**. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on **users, developers, and relay operators**. If you believe in **free speech, decentralization, and an open internet**, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, **every effort helps build a more robust network**. Here’s how you can get involved and make a difference. --- ## **1️⃣ Use Nostr Daily** The simplest and most effective way to contribute to Nostr is by **using it regularly**. The more active users, the stronger and more valuable the network becomes. ✅ **Post, comment, and zap** (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ **Engage with new users** and help them understand how Nostr works.\ ✅ **Try different Nostr clients** like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience. Your activity **keeps the network alive** and helps encourage more developers and relay operators to invest in the ecosystem. --- ## **2️⃣ Run Your Own Nostr Relay** Relays are the **backbone of Nostr**, responsible for distributing messages across the network. The more **independent relays exist**, the stronger and more censorship-resistant Nostr becomes. ✅ **Set up your own relay** to help decentralize the network further.\ ✅ **Experiment with relay configurations** and different performance optimizations.\ ✅ **Offer public or private relay services** to users looking for high-quality infrastructure. If you're not technical, you can still **support relay operators** by **subscribing to a paid relay** or donating to open-source relay projects. --- ## **3️⃣ Support Paid Relays & Infrastructure** Free relays have helped Nostr grow, but they **struggle with spam, slow speeds, and sustainability issues**. **Paid relays** help fund **better infrastructure, faster message delivery, and a more reliable experience**. ✅ **Subscribe to a paid relay** to help keep it running.\ ✅ **Use premium services** like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ **Donate to relay operators** who invest in long-term infrastructure. By funding **Nostr’s decentralized backbone**, you help ensure its **longevity and reliability**. --- ## **4️⃣ Zap Developers, Creators & Builders** Many people contribute to Nostr **without direct financial compensation**—developers who build clients, relay operators, educators, and content creators. **You can support them with zaps!** ⚡ ✅ **Find developers working on Nostr projects** and send them a zap.\ ✅ **Support content creators and educators** who spread awareness about Nostr.\ ✅ **Encourage builders** by donating to open-source projects. Micro-payments via the **Lightning Network** make it easy to directly **support the people who make Nostr better**. --- ## **5️⃣ Develop New Nostr Apps & Tools** If you're a developer, you can **build on Nostr’s open protocol** to create new apps, bots, or tools. Nostr is **permissionless**, meaning anyone can develop for it. ✅ **Create new Nostr clients** with unique features and user experiences.\ ✅ **Build bots or automation tools** that improve engagement and usability.\ ✅ **Experiment with decentralized identity, authentication, and encryption** to make Nostr even stronger. With **no corporate gatekeepers**, your projects can help shape the future of decentralized social media. --- ## **6️⃣ Promote & Educate Others About Nostr** Adoption grows when **more people understand and use Nostr**. You can help by **spreading awareness** and creating educational content. ✅ **Write blogs, guides, and tutorials** explaining how to use Nostr.\ ✅ **Make videos or social media posts** introducing new users to the protocol.\ ✅ **Host discussions, Twitter Spaces, or workshops** to onboard more people. The more people **understand and trust Nostr**, the stronger the ecosystem becomes. --- ## **7️⃣ Support Open-Source Nostr Projects** Many Nostr tools and clients are **built by volunteers**, and open-source projects thrive on **community support**. ✅ **Contribute code** to existing Nostr projects on GitHub.\ ✅ **Report bugs and suggest features** to improve Nostr clients.\ ✅ **Donate to developers** who keep Nostr free and open for everyone. If you're not a developer, you can still **help with testing, translations, and documentation** to make projects more accessible. --- ## **🚀 Every Contribution Strengthens Nostr** Whether you: ✔️ **Post and engage daily**\ ✔️ **Zap creators and developers**\ ✔️ **Run or support relays**\ ✔️ **Build new apps and tools**\ ✔️ **Educate and onboard new users** **Every action helps make Nostr more resilient, decentralized, and unstoppable.** Nostr isn’t just another social network—it’s **a movement toward a free and open internet**. If you believe in **digital freedom, privacy, and decentralization**, now is the time to get involved. @ 16f1a010:31b1074b
2025-02-19 20:57:59In the rapidly evolving world of Bitcoin, running a Bitcoin node has become more accessible than ever. Platforms like Umbrel, Start9, myNode, and Citadel offer user-friendly interfaces to simplify node management. However, for those serious about maintaining a robust and efficient Lightning node ⚡, relying solely on these platforms may not be the optimal choice. Let’s delve into why embracing **Bitcoin Core** and mastering the command-line interface (CLI) can provide a **more reliable, sovereign, and empowering** experience. ### Understanding Node Management Platforms #### What Are Umbrel, Start9, myNode, and Citadel? Umbrel, Start9, myNode, and Citadel are platforms designed to streamline the process of running a Bitcoin node. They offer graphical user interfaces (GUIs) that allow users to manage various applications, including Bitcoin Core and Lightning Network nodes, through a web-based dashboard 🖥️. These platforms often utilize Docker containers 🐳 to encapsulate applications, providing a modular and isolated environment for each service.  #### The Appeal of Simplified Node Management The primary allure of these platforms lies in their simplicity. With minimal command-line interaction, users can deploy a full Bitcoin and Lightning node, along with a suite of additional applications. ✅ **Easy one-command installation** ✅ **Web-based GUI for management** ✅ **Automatic app updates** *(but with delays, as we’ll discuss)* However, while this convenience is attractive, it comes **at a cost**. ### The Hidden Complexities of Using Node Management Platforms While the user-friendly nature of these platforms is advantageous, it can also introduce several challenges that may hinder advanced users or those seeking greater control over their nodes. #### 🚨 Dependency on Maintainers for Updates One significant concern is the reliance on platform maintainers for updates. Since these platforms manage applications through Docker containers, users must wait for the maintainers to update the container images before they can access new features or security patches. 🔴 **Delayed Bitcoin Core updates = potential security risks** 🔴 **Lightning Network updates are not immediate** 🔴 **Bugs and vulnerabilities may persist longer** Instead of waiting on a third party, **why not update Bitcoin Core & LND yourself instantly**? #### ⚙️ Challenges in Customization and Advanced Operations For users aiming to perform advanced operations, such as: * Custom backups 📂 * Running specific CLI commands 🖥️ * Optimizing node settings ⚡ …the **abstraction layers introduced by these platforms become obstacles**. Navigating through nested directories and issuing commands inside Docker containers **makes troubleshooting a nightmare**. Instead of a simple `bitcoin-cli` command, you must figure out how to execute it inside the container, adding unnecessary complexity. #### Increased Backend Complexity To achieve **frontend simplicity**, these platforms make the backend more complex. 🚫 Extra layers of abstraction 🚫 Hidden logs and settings 🚫 Harder troubleshooting The use of **multiple Docker containers**, **custom scripts**, and **unique file structures** can **make system maintenance and debugging a pain**. This **complication defeats the purpose** of “making running a node easy.” ## ✅ Advantages of Using Bitcoin Core and Command-Line Interface (CLI) By installing Bitcoin Core directly and using the command-line interface (CLI), you gain several key advantages that make managing a Bitcoin and Lightning node more efficient and empowering. #### Direct Control and Immediate Updates One of the biggest downsides of package manager-based platforms is the reliance on third-party maintainers to release updates. Since Bitcoin Core, Lightning implementations (such as LND, Core Lightning, or Eclair), and other related software evolve rapidly, waiting for platform-specific updates can leave you running outdated or vulnerable versions. By installing Bitcoin Core directly, you remove this dependency. You can update immediately when new versions are released, ensuring your node benefits from the latest features, security patches, and bug fixes. The same applies to Lightning software—being able to install and update it yourself gives you full autonomy over your node’s performance and security. #### 🛠 Simplified System Architecture Platforms like Umbrel and myNode introduce extra complexity by running Bitcoin Core and Lightning inside Docker containers. This means: * The actual files and configurations are stored inside Docker’s filesystem, making it **harder to locate and manage them manually**. * If something breaks, **troubleshooting is more difficult** due to the added layer of abstraction. * Running commands requires jumping through Docker shell sessions, adding unnecessary friction to what should be a straightforward process. Instead, a direct installation of Bitcoin Core, Lightning, and Electrum Server (if needed) results in a **cleaner, more understandable system**. The software runs natively on your machine, without containerized layers making things more convoluted. Additionally, setting up your own systemd service files for Bitcoin and Lightning** is not as complicated as it seems**. Once configured, these services will run automatically on boot, offering the same level of convenience as platforms like Umbrel but without the unnecessary complexity. #### Better Lightning Node Management If you’re running a **Lightning Network node**, using CLI-based tools provides far more flexibility than relying on a GUI like the ones bundled with node management platforms. 🟢 **Custom Backup Strategies** – Running Lightning through a GUI-based node manager often means backups are handled in a way that is opaque to the user. With CLI tools, you can easily script automatic backups of your channels, wallets, and configurations. 🟢 **Advanced Configuration** – Platforms like Umbrel force certain configurations by default, limiting how you can customize your Lightning node. With a direct install, you have full control over: * Channel fees 💰 * Routing policies 📡 * Liquidity management 🔄 🟢 **Direct Access to LND, Core Lightning, or Eclair** – Instead of issuing commands through a GUI (which is often limited in functionality), you can use: * `lncli` (for LND) * `lightning-cli` (for Core Lightning) …to interact with your node at a deeper level. #### Enhanced Learning and Engagement A crucial aspect of running a Bitcoin and Lightning node is **understanding how it works**. Using an abstraction layer like Umbrel may get a node running in a few clicks, but **it does little to teach users how Bitcoin actually functions**. By setting up Bitcoin Core, Lightning, and related software manually, you will: ✅ Gain practical knowledge of Bitcoin nodes, networking, and system performance. ✅ Learn how to configure and manage RPC commands. ✅ Become less reliant on third-party developers and more confident in troubleshooting. 🎯 **Running a Bitcoin node is about sovereignty – learn how to control it yourself**. ## Become more sovereign TODAY Many guides make this process **straightforward** [K3tan](https://k3tan.com/about) has a fantastic guide on running Bitcoin Core, Electrs, LND and more. - [Ministry of Nodes Guide 2024](https://www.youtube.com/playlist?list=PLCRbH-IWlcW0g0HCrtI06_ZdVVolUWr39) - You can find him on nostr nostr:npub1txwy7guqkrq6ngvtwft7zp70nekcknudagrvrryy2wxnz8ljk2xqz0yt4x Even with the best of guides, if you are running this software, 📖 **READ THE DOCUMENTATION** This is all just software at the end of the day. Most of it is very well documented. Take a moment to actually read through the documentation for yourself when installing. The documentation has step by step guides on setting up the software. Here is a helpful list: * [Bitcoin.org Bitcoin Core Linux install instructions](https://bitcoin.org/en/full-node#linux-instructions) * [Bitcoin Core Code Repository](https://github.com/bitcoin/bitcoin) * [Electrs Installation](https://github.com/romanz/electrs/blob/master/doc/install.md) * [LND Documentation](https://docs.lightning.engineering/) * [LND Code Repository](https://github.com/lightningnetwork/lnd) * [CLN Documentation](https://docs.corelightning.org/docs/home) * [CLN Code Repository](https://github.com/ElementsProject/lightning) *If you have any more resources or links I should add, please comment them . I want to add as much to this article as I can.*
@ 16f1a010:31b1074b
2025-02-19 20:57:59In the rapidly evolving world of Bitcoin, running a Bitcoin node has become more accessible than ever. Platforms like Umbrel, Start9, myNode, and Citadel offer user-friendly interfaces to simplify node management. However, for those serious about maintaining a robust and efficient Lightning node ⚡, relying solely on these platforms may not be the optimal choice. Let’s delve into why embracing **Bitcoin Core** and mastering the command-line interface (CLI) can provide a **more reliable, sovereign, and empowering** experience. ### Understanding Node Management Platforms #### What Are Umbrel, Start9, myNode, and Citadel? Umbrel, Start9, myNode, and Citadel are platforms designed to streamline the process of running a Bitcoin node. They offer graphical user interfaces (GUIs) that allow users to manage various applications, including Bitcoin Core and Lightning Network nodes, through a web-based dashboard 🖥️. These platforms often utilize Docker containers 🐳 to encapsulate applications, providing a modular and isolated environment for each service.  #### The Appeal of Simplified Node Management The primary allure of these platforms lies in their simplicity. With minimal command-line interaction, users can deploy a full Bitcoin and Lightning node, along with a suite of additional applications. ✅ **Easy one-command installation** ✅ **Web-based GUI for management** ✅ **Automatic app updates** *(but with delays, as we’ll discuss)* However, while this convenience is attractive, it comes **at a cost**. ### The Hidden Complexities of Using Node Management Platforms While the user-friendly nature of these platforms is advantageous, it can also introduce several challenges that may hinder advanced users or those seeking greater control over their nodes. #### 🚨 Dependency on Maintainers for Updates One significant concern is the reliance on platform maintainers for updates. Since these platforms manage applications through Docker containers, users must wait for the maintainers to update the container images before they can access new features or security patches. 🔴 **Delayed Bitcoin Core updates = potential security risks** 🔴 **Lightning Network updates are not immediate** 🔴 **Bugs and vulnerabilities may persist longer** Instead of waiting on a third party, **why not update Bitcoin Core & LND yourself instantly**? #### ⚙️ Challenges in Customization and Advanced Operations For users aiming to perform advanced operations, such as: * Custom backups 📂 * Running specific CLI commands 🖥️ * Optimizing node settings ⚡ …the **abstraction layers introduced by these platforms become obstacles**. Navigating through nested directories and issuing commands inside Docker containers **makes troubleshooting a nightmare**. Instead of a simple `bitcoin-cli` command, you must figure out how to execute it inside the container, adding unnecessary complexity. #### Increased Backend Complexity To achieve **frontend simplicity**, these platforms make the backend more complex. 🚫 Extra layers of abstraction 🚫 Hidden logs and settings 🚫 Harder troubleshooting The use of **multiple Docker containers**, **custom scripts**, and **unique file structures** can **make system maintenance and debugging a pain**. This **complication defeats the purpose** of “making running a node easy.” ## ✅ Advantages of Using Bitcoin Core and Command-Line Interface (CLI) By installing Bitcoin Core directly and using the command-line interface (CLI), you gain several key advantages that make managing a Bitcoin and Lightning node more efficient and empowering. #### Direct Control and Immediate Updates One of the biggest downsides of package manager-based platforms is the reliance on third-party maintainers to release updates. Since Bitcoin Core, Lightning implementations (such as LND, Core Lightning, or Eclair), and other related software evolve rapidly, waiting for platform-specific updates can leave you running outdated or vulnerable versions. By installing Bitcoin Core directly, you remove this dependency. You can update immediately when new versions are released, ensuring your node benefits from the latest features, security patches, and bug fixes. The same applies to Lightning software—being able to install and update it yourself gives you full autonomy over your node’s performance and security. #### 🛠 Simplified System Architecture Platforms like Umbrel and myNode introduce extra complexity by running Bitcoin Core and Lightning inside Docker containers. This means: * The actual files and configurations are stored inside Docker’s filesystem, making it **harder to locate and manage them manually**. * If something breaks, **troubleshooting is more difficult** due to the added layer of abstraction. * Running commands requires jumping through Docker shell sessions, adding unnecessary friction to what should be a straightforward process. Instead, a direct installation of Bitcoin Core, Lightning, and Electrum Server (if needed) results in a **cleaner, more understandable system**. The software runs natively on your machine, without containerized layers making things more convoluted. Additionally, setting up your own systemd service files for Bitcoin and Lightning** is not as complicated as it seems**. Once configured, these services will run automatically on boot, offering the same level of convenience as platforms like Umbrel but without the unnecessary complexity. #### Better Lightning Node Management If you’re running a **Lightning Network node**, using CLI-based tools provides far more flexibility than relying on a GUI like the ones bundled with node management platforms. 🟢 **Custom Backup Strategies** – Running Lightning through a GUI-based node manager often means backups are handled in a way that is opaque to the user. With CLI tools, you can easily script automatic backups of your channels, wallets, and configurations. 🟢 **Advanced Configuration** – Platforms like Umbrel force certain configurations by default, limiting how you can customize your Lightning node. With a direct install, you have full control over: * Channel fees 💰 * Routing policies 📡 * Liquidity management 🔄 🟢 **Direct Access to LND, Core Lightning, or Eclair** – Instead of issuing commands through a GUI (which is often limited in functionality), you can use: * `lncli` (for LND) * `lightning-cli` (for Core Lightning) …to interact with your node at a deeper level. #### Enhanced Learning and Engagement A crucial aspect of running a Bitcoin and Lightning node is **understanding how it works**. Using an abstraction layer like Umbrel may get a node running in a few clicks, but **it does little to teach users how Bitcoin actually functions**. By setting up Bitcoin Core, Lightning, and related software manually, you will: ✅ Gain practical knowledge of Bitcoin nodes, networking, and system performance. ✅ Learn how to configure and manage RPC commands. ✅ Become less reliant on third-party developers and more confident in troubleshooting. 🎯 **Running a Bitcoin node is about sovereignty – learn how to control it yourself**. ## Become more sovereign TODAY Many guides make this process **straightforward** [K3tan](https://k3tan.com/about) has a fantastic guide on running Bitcoin Core, Electrs, LND and more. - [Ministry of Nodes Guide 2024](https://www.youtube.com/playlist?list=PLCRbH-IWlcW0g0HCrtI06_ZdVVolUWr39) - You can find him on nostr nostr:npub1txwy7guqkrq6ngvtwft7zp70nekcknudagrvrryy2wxnz8ljk2xqz0yt4x Even with the best of guides, if you are running this software, 📖 **READ THE DOCUMENTATION** This is all just software at the end of the day. Most of it is very well documented. Take a moment to actually read through the documentation for yourself when installing. The documentation has step by step guides on setting up the software. Here is a helpful list: * [Bitcoin.org Bitcoin Core Linux install instructions](https://bitcoin.org/en/full-node#linux-instructions) * [Bitcoin Core Code Repository](https://github.com/bitcoin/bitcoin) * [Electrs Installation](https://github.com/romanz/electrs/blob/master/doc/install.md) * [LND Documentation](https://docs.lightning.engineering/) * [LND Code Repository](https://github.com/lightningnetwork/lnd) * [CLN Documentation](https://docs.corelightning.org/docs/home) * [CLN Code Repository](https://github.com/ElementsProject/lightning) *If you have any more resources or links I should add, please comment them . I want to add as much to this article as I can.* @ 266815e0:6cd408a5
2025-02-18 17:25:31## noStrudel Released another major version of noStrudel v0.42.0 Which included a few new features and a lot of cleanup nostr:naddr1qvzqqqr4gupzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqp3hx7um5wf6kgetv956ry6rmhwr ## Blossom On the blossom front there where a few more PRs - Expanded the documentation around CORS headers in BUD-01 thanks to nostr:npub1a6we08n7zsv2na689whc9hykpq4q6sj3kaauk9c2dm8vj0adlajq7w0tyc - Made auth optional on the `/upload` endpoint [PR](https://github.com/hzrd149/blossom/pull/33) - Added a `HEAD /media` endpoint for BUD-05 [PR](https://github.com/hzrd149/blossom/pull/42) - Added range request recommendations to BUD-01 [PR](https://github.com/hzrd149/blossom/pull/47) With blossom uploads starting to be supported in more nostr clients users where starting to ask where to find a list of blossom servers. so I created a simple nostr client that allows users to post servers and leave reviews [blossomservers.com](https://blossomservers.com) Its still very much a work in progress (needs login and server and review editing) The source is on [github](https://github.com/hzrd149/blossomservers) I also started another project to create a simple account based paid blossom server [blossom-account-server](https://github.com/hzrd149/blossom-account-server) Unfortunately I got sidetracked and I didn't have the time to give it the attention it needs to get it over the finish line ## Smaller projects - [cherry-tree](https://github.com/hzrd149/cherry-tree) A small app for uploading chunked blobs to blossom servers (with cashu payment support) - [vite-plugin-funding](https://github.com/hzrd149/vite-plugin-funding) A vite plugin to collect and expose package "funding" to the app - [node-red-contrib-rx-nostr](https://github.com/hzrd149/node-red-contrib-rx-nostr) The start of a node-red package for rx-nostr. if your interested please help - [node-red-contrib-applesauce](https://github.com/hzrd149/node-red-contrib-applesauce) The start of a node-red package for applesauce. I probably wont finish it so any help it welcome ## Plans for 2025 I have a few vague ideas of what I want to work on Q1 of 2025. but there are a few things i know for certain. I'm going to keep refactoring noStrudel by moving core logic out into [applesauce](https://hzrd149.github.io/applesauce/) and making it more modular. This should make noStrudel more reliable and hopefully allow me to create and maintain more apps with less code And I'm going to write tests. tests for everything. hopefully tests for all the libraries and apps I've created in 2024. A lot of the code I wrote in 2024 was hacky code to see if things could work. and while its been working pretty well I'm starting to forget the details of of the code I wrote so I cant be sure if it still works or how well it works. So my solution is to write tests, lots of tests :)
@ 266815e0:6cd408a5
2025-02-18 17:25:31## noStrudel Released another major version of noStrudel v0.42.0 Which included a few new features and a lot of cleanup nostr:naddr1qvzqqqr4gupzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqp3hx7um5wf6kgetv956ry6rmhwr ## Blossom On the blossom front there where a few more PRs - Expanded the documentation around CORS headers in BUD-01 thanks to nostr:npub1a6we08n7zsv2na689whc9hykpq4q6sj3kaauk9c2dm8vj0adlajq7w0tyc - Made auth optional on the `/upload` endpoint [PR](https://github.com/hzrd149/blossom/pull/33) - Added a `HEAD /media` endpoint for BUD-05 [PR](https://github.com/hzrd149/blossom/pull/42) - Added range request recommendations to BUD-01 [PR](https://github.com/hzrd149/blossom/pull/47) With blossom uploads starting to be supported in more nostr clients users where starting to ask where to find a list of blossom servers. so I created a simple nostr client that allows users to post servers and leave reviews [blossomservers.com](https://blossomservers.com) Its still very much a work in progress (needs login and server and review editing) The source is on [github](https://github.com/hzrd149/blossomservers) I also started another project to create a simple account based paid blossom server [blossom-account-server](https://github.com/hzrd149/blossom-account-server) Unfortunately I got sidetracked and I didn't have the time to give it the attention it needs to get it over the finish line ## Smaller projects - [cherry-tree](https://github.com/hzrd149/cherry-tree) A small app for uploading chunked blobs to blossom servers (with cashu payment support) - [vite-plugin-funding](https://github.com/hzrd149/vite-plugin-funding) A vite plugin to collect and expose package "funding" to the app - [node-red-contrib-rx-nostr](https://github.com/hzrd149/node-red-contrib-rx-nostr) The start of a node-red package for rx-nostr. if your interested please help - [node-red-contrib-applesauce](https://github.com/hzrd149/node-red-contrib-applesauce) The start of a node-red package for applesauce. I probably wont finish it so any help it welcome ## Plans for 2025 I have a few vague ideas of what I want to work on Q1 of 2025. but there are a few things i know for certain. I'm going to keep refactoring noStrudel by moving core logic out into [applesauce](https://hzrd149.github.io/applesauce/) and making it more modular. This should make noStrudel more reliable and hopefully allow me to create and maintain more apps with less code And I'm going to write tests. tests for everything. hopefully tests for all the libraries and apps I've created in 2024. A lot of the code I wrote in 2024 was hacky code to see if things could work. and while its been working pretty well I'm starting to forget the details of of the code I wrote so I cant be sure if it still works or how well it works. So my solution is to write tests, lots of tests :) @ fd208ee8:0fd927c1
2025-02-15 07:37:01E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats". They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable. It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions. What we then have is * a **transaction on a relay** that triggers * a **transaction on a mint** that triggers * a **transaction on Lightning** that triggers * a **transaction on Bitcoin**. Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted. There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself. https://github.com/nostr-protocol/nips/blob/master/60.md https://github.com/nostr-protocol/nips/blob/master/61.md
@ fd208ee8:0fd927c1
2025-02-15 07:37:01E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats". They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable. It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions. What we then have is * a **transaction on a relay** that triggers * a **transaction on a mint** that triggers * a **transaction on Lightning** that triggers * a **transaction on Bitcoin**. Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted. There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself. https://github.com/nostr-protocol/nips/blob/master/60.md https://github.com/nostr-protocol/nips/blob/master/61.md @ 19220736:7578e0e9
2025-02-14 03:44:21While Zelle promotes itself as a quick and easy way to send money, its instant, irreversible transactions have made it a prime target for fraudsters. Despite mounting reports of consumer losses, banks continue to deny reimbursement for many fraud victims, citing narrow legal loopholes. Meanwhile, Early Warning Services, the company behind Zelle, profits from the vast consumer data it collects, fueling concerns about privacy and corporate exploitation. With government investigations ramping up and public pressure mounting, Zelle and their bank owners have teamed up with the Aspen Institute, forming a new task force with corporate and government players. In 2017, [Early Warning Services](https://www.earlywarning.com/about), owned by Bank of America, Capital One, JPMorgan Chase, PNC Bank, Trust, U.S. Bank, and Wells Fargo, released the [Zelle](https://www.zellepay.com/faq/what-zelle) payment system. It was a fast way to send and receive funds peer to peer between different bank accounts by only needing either the other person's email address or their U.S. mobile phone number. By 2018, there were growing [concerns](https://www.nytimes.com/2018/04/22/business/zelle-banks-fraud.html) about fraud on Zelle. Despite its convenience, Zelle's design allows funds to transfer instantly and irreversibly, making it a target for scammers. Victims reported being defrauded through tactics like fake online sales or impersonation schemes, and many struggled to recover lost funds due to inconsistent fraud policies among banks. Consumer advocates criticized the platform for inadequate protections, urging banks to implement stronger safeguards to prevent fraud and better support affected customers. In 2022, a Senate report [criticized](https://www.bankingdive.com/news/warren-zelle-fraud-scams-report-truist-pnc-us-bank-america-jpmorgan-wells-fargo-aba-bpi-cba/633305/) major U.S. banks, including JPMorgan Chase, Bank of America, and Wells Fargo, for failing to adequately protect consumers from fraud on the Zelle payment platform. The investigation revealed that these banks often deny reimbursement for scams where victims are tricked into transferring funds, citing a narrow interpretation of liability under the Electronic Fund Transfer Act. (*"While banks bear responsibility for unauthorized transactions to scammers, consumer-authorized transactions made to fraudsters are another matter”*.) Jamie Dimon, CEO of JPMorgan Chase, [explained](https://www.bankingdive.com/news/bank-ceos-defend-zelle-in-senate-hearing/632554/), *“Anything unauthorized, we do cover”* On June 16, 2023, the United States Senate Committee on Homeland Security and Governmental Affairs subcommittee, the Permanent Subcommittee on Investigations, launched an inquiry into Early Warning Services and the three largest banks that co-own EWS: JPMorgan Chase, Bank of America, and Wells Fargo. After a 15-month investigation, the Senate Permanent Subcommittee on Investigations released a [report](https://www.hsgac.senate.gov/wp-content/uploads/2024.7.23-PSI-Majority-Staff-Report-on-Zelle.pdf) on July 23, 2024, highlighting consumer fraud issues tied to the Zelle payment network. The report noted significant drops in the percentage of fraud disputes reimbursed—from 62% in 2019 to just 38% in 2023. Between 2021 and 2023 Zelle [refused](https://dailyhodl.com/2024/07/25/jpmorgan-chase-wells-fargo-and-bank-of-america-refuse-to-reimburse-863000000-to-customers-in-repeated-relentless-failure-to-protect-victims-of-fraud-us-senate-investigation/) to reimburse $880 million to customers who fell victim to fraud on their payment network. Bank employees were found to have broad discretion in deciding whether to reimburse fraud claims, often denying compensation without clear justification. This has raised questions about whether banks are meeting legal obligations under the Electronic Fund Transfer Act ([Regulation E](https://www.consumerfinance.gov/rules-policy/regulations/1005/)) Early Warning Services (EWS) runs the payment network Zelle at a financial loss but generates revenue by selling data-based services to financial institutions. EWS collects extensive consumer and bank data through its operation of Zelle and daily data-sharing agreements with its member banks. This data is used to develop fraud and risk management products, which EWS sells to financial institutions as its primary profit source. While EWS asserts it has not commercialized this data beyond these financial products, the sale of such services remains its main revenue driver. On August 4, 2024, Senator Richard Blumenthal sent a [letter](https://www.hsgac.senate.gov/wp-content/uploads/2024.08.04-Blumenthal-Letter-to-Chopra.pdf) to CFPB Director Rohit Chopra urging immediate action to address fraud concerns tied to the Zelle payment platform. The letter calls for the Consumer Financial Protection Bureau (CFPB) to investigate their dispute resolution practices and ensure that they fully and promptly address consumer fraud reports. On August 7, 2024, it was [reported](https://www.reuters.com/business/finance/us-consumer-watchdog-probes-major-us-banks-over-zelle-scam-wsj-reports-2024-08-07/) that the Consumer Financial Protection Bureau was investigating several banks due to their handling of Zelle. On December 20, 2024, The Consumer Financial Protection Bureau (CFPB) responded by [filing](https://files.consumerfinance.gov/f/documents/cfpb_Zelle-Complaint_2024-12.pdf) a lawsuit against Early Warning Services, LLC and the major banks including Bank of America, JPMorgan Chase, and Wells Fargo. The CFPB alleges that these institutions prioritized the rapid deployment of Zelle over implementing effective anti-fraud measures, resulting in significant consumer losses. The lawsuit contends that the defendants failed to adequately address these issues, often denying relief to defrauded consumers. The CFPB seeks injunctive relief, monetary compensation for affected consumers, and civil penalties. Just 5 days before the Senate Permanent Subcommittee on Investigations released its report, the [Aspen Institute](https://www.aspeninstitute.org/) Financial Security Program (Aspen FSP) [announced](https://www.aspeninstitute.org/news/task-force-on-fraud-and-scams/) the formation of a National Task Force for Fraud & Scam Prevention with their founding sponsor JPMorganChase and executive sponsor Zelle. The stated purpose of the Task Force is to develop a unified national strategy to help the U.S. government and private sector companies work together to stop fraud and scams. [Members](https://fraudtaskforce.aspeninstitute.org/membership) of this private/public task force include: JPMorgan Chase, Bank of America, Wells Fargo, Google, Meta, Amazon, Visa, Mastercard, Verizon, the Federal Trade Commission, the FBI Criminal Investigation Unit, US Department of the Treasury, Homeland Security, and many others. The Aspen Institute is a 501(c)(3) nonprofit located in Washington DC. In [2023](https://projects.propublica.org/nonprofits/organizations/840399006) they had revenue of $232M and total assets of $519M with the primary source of income coming from donations and federal grants. Per their [mission](https://www.aspeninstitute.org/what-we-do/) statement, their goal is "realizing a free, just, and equitable society." The Institute works to achieve this through creating and driving policy as well as training future policy leaders. Recently on November 25, 2024, FinCen [announced](https://www.fincen.gov/news/news-releases/fincen-joins-public-private-partnership-combat-fraud-and-scams-impacting) they are also joining the National Task Force that *"brings together key stakeholders including the financial services sector, technology companies, consumer advocacy groups, information sharing and analysis centers, and federal government agencies to develop a comprehensive national strategy for combating fraud and scams."* In The Case for a Coordinated National Strategy to Prevent Fraud and Scams, the Task Force lists [key components](https://fraudtaskforce.aspeninstitute.org/time-is-now) of a national strategy to include improved education of consumers to identify fraud, enhanced information sharing across industry, law enforcement, and regulatory agencies by use of data exchanges and legal mechanisms for sharing information. As well as empowering law enforcement with additional authority and resources. The document cites the recent [UK action](https://www.gov.uk/government/news/new-powers-to-seize-cryptoassets-used-by-criminals-go-live) as an example of recent amendments to law enforcement powers which in England means police will no longer be required to arrest seizing crypto from a suspect, can seize written passwords or memory sticks, as well as transfer "crypto assets" to a law enforcement wallet. In an August 2024 [interview](https://www.businessinsider.com/zelle-scams-how-to-get-money-back-2024-8?) with Fortune, Ben Chance, the Chief Fraud Risk Management Officer for Early Warning Services reportedly "told the outlet that the best way to prevent scams on money-sharing apps is better user education, sound policy and more funding for law enforcement." This sounds very similar to the National Strategy to Prevent Fraud and Scams being crafted by the National Task Force for Fraud & Scam Prevention, with more user education and law enforcement. No mention of standardized reimbursement policies or enhancing transparency around fraud investigations which are the primary accusations aimed at Zelle and its owners by the US Senate and the subject of the current investigation by the Consumer Financial Protection Bureau.
@ 19220736:7578e0e9
2025-02-14 03:44:21While Zelle promotes itself as a quick and easy way to send money, its instant, irreversible transactions have made it a prime target for fraudsters. Despite mounting reports of consumer losses, banks continue to deny reimbursement for many fraud victims, citing narrow legal loopholes. Meanwhile, Early Warning Services, the company behind Zelle, profits from the vast consumer data it collects, fueling concerns about privacy and corporate exploitation. With government investigations ramping up and public pressure mounting, Zelle and their bank owners have teamed up with the Aspen Institute, forming a new task force with corporate and government players. In 2017, [Early Warning Services](https://www.earlywarning.com/about), owned by Bank of America, Capital One, JPMorgan Chase, PNC Bank, Trust, U.S. Bank, and Wells Fargo, released the [Zelle](https://www.zellepay.com/faq/what-zelle) payment system. It was a fast way to send and receive funds peer to peer between different bank accounts by only needing either the other person's email address or their U.S. mobile phone number. By 2018, there were growing [concerns](https://www.nytimes.com/2018/04/22/business/zelle-banks-fraud.html) about fraud on Zelle. Despite its convenience, Zelle's design allows funds to transfer instantly and irreversibly, making it a target for scammers. Victims reported being defrauded through tactics like fake online sales or impersonation schemes, and many struggled to recover lost funds due to inconsistent fraud policies among banks. Consumer advocates criticized the platform for inadequate protections, urging banks to implement stronger safeguards to prevent fraud and better support affected customers. In 2022, a Senate report [criticized](https://www.bankingdive.com/news/warren-zelle-fraud-scams-report-truist-pnc-us-bank-america-jpmorgan-wells-fargo-aba-bpi-cba/633305/) major U.S. banks, including JPMorgan Chase, Bank of America, and Wells Fargo, for failing to adequately protect consumers from fraud on the Zelle payment platform. The investigation revealed that these banks often deny reimbursement for scams where victims are tricked into transferring funds, citing a narrow interpretation of liability under the Electronic Fund Transfer Act. (*"While banks bear responsibility for unauthorized transactions to scammers, consumer-authorized transactions made to fraudsters are another matter”*.) Jamie Dimon, CEO of JPMorgan Chase, [explained](https://www.bankingdive.com/news/bank-ceos-defend-zelle-in-senate-hearing/632554/), *“Anything unauthorized, we do cover”* On June 16, 2023, the United States Senate Committee on Homeland Security and Governmental Affairs subcommittee, the Permanent Subcommittee on Investigations, launched an inquiry into Early Warning Services and the three largest banks that co-own EWS: JPMorgan Chase, Bank of America, and Wells Fargo. After a 15-month investigation, the Senate Permanent Subcommittee on Investigations released a [report](https://www.hsgac.senate.gov/wp-content/uploads/2024.7.23-PSI-Majority-Staff-Report-on-Zelle.pdf) on July 23, 2024, highlighting consumer fraud issues tied to the Zelle payment network. The report noted significant drops in the percentage of fraud disputes reimbursed—from 62% in 2019 to just 38% in 2023. Between 2021 and 2023 Zelle [refused](https://dailyhodl.com/2024/07/25/jpmorgan-chase-wells-fargo-and-bank-of-america-refuse-to-reimburse-863000000-to-customers-in-repeated-relentless-failure-to-protect-victims-of-fraud-us-senate-investigation/) to reimburse $880 million to customers who fell victim to fraud on their payment network. Bank employees were found to have broad discretion in deciding whether to reimburse fraud claims, often denying compensation without clear justification. This has raised questions about whether banks are meeting legal obligations under the Electronic Fund Transfer Act ([Regulation E](https://www.consumerfinance.gov/rules-policy/regulations/1005/)) Early Warning Services (EWS) runs the payment network Zelle at a financial loss but generates revenue by selling data-based services to financial institutions. EWS collects extensive consumer and bank data through its operation of Zelle and daily data-sharing agreements with its member banks. This data is used to develop fraud and risk management products, which EWS sells to financial institutions as its primary profit source. While EWS asserts it has not commercialized this data beyond these financial products, the sale of such services remains its main revenue driver. On August 4, 2024, Senator Richard Blumenthal sent a [letter](https://www.hsgac.senate.gov/wp-content/uploads/2024.08.04-Blumenthal-Letter-to-Chopra.pdf) to CFPB Director Rohit Chopra urging immediate action to address fraud concerns tied to the Zelle payment platform. The letter calls for the Consumer Financial Protection Bureau (CFPB) to investigate their dispute resolution practices and ensure that they fully and promptly address consumer fraud reports. On August 7, 2024, it was [reported](https://www.reuters.com/business/finance/us-consumer-watchdog-probes-major-us-banks-over-zelle-scam-wsj-reports-2024-08-07/) that the Consumer Financial Protection Bureau was investigating several banks due to their handling of Zelle. On December 20, 2024, The Consumer Financial Protection Bureau (CFPB) responded by [filing](https://files.consumerfinance.gov/f/documents/cfpb_Zelle-Complaint_2024-12.pdf) a lawsuit against Early Warning Services, LLC and the major banks including Bank of America, JPMorgan Chase, and Wells Fargo. The CFPB alleges that these institutions prioritized the rapid deployment of Zelle over implementing effective anti-fraud measures, resulting in significant consumer losses. The lawsuit contends that the defendants failed to adequately address these issues, often denying relief to defrauded consumers. The CFPB seeks injunctive relief, monetary compensation for affected consumers, and civil penalties. Just 5 days before the Senate Permanent Subcommittee on Investigations released its report, the [Aspen Institute](https://www.aspeninstitute.org/) Financial Security Program (Aspen FSP) [announced](https://www.aspeninstitute.org/news/task-force-on-fraud-and-scams/) the formation of a National Task Force for Fraud & Scam Prevention with their founding sponsor JPMorganChase and executive sponsor Zelle. The stated purpose of the Task Force is to develop a unified national strategy to help the U.S. government and private sector companies work together to stop fraud and scams. [Members](https://fraudtaskforce.aspeninstitute.org/membership) of this private/public task force include: JPMorgan Chase, Bank of America, Wells Fargo, Google, Meta, Amazon, Visa, Mastercard, Verizon, the Federal Trade Commission, the FBI Criminal Investigation Unit, US Department of the Treasury, Homeland Security, and many others. The Aspen Institute is a 501(c)(3) nonprofit located in Washington DC. In [2023](https://projects.propublica.org/nonprofits/organizations/840399006) they had revenue of $232M and total assets of $519M with the primary source of income coming from donations and federal grants. Per their [mission](https://www.aspeninstitute.org/what-we-do/) statement, their goal is "realizing a free, just, and equitable society." The Institute works to achieve this through creating and driving policy as well as training future policy leaders. Recently on November 25, 2024, FinCen [announced](https://www.fincen.gov/news/news-releases/fincen-joins-public-private-partnership-combat-fraud-and-scams-impacting) they are also joining the National Task Force that *"brings together key stakeholders including the financial services sector, technology companies, consumer advocacy groups, information sharing and analysis centers, and federal government agencies to develop a comprehensive national strategy for combating fraud and scams."* In The Case for a Coordinated National Strategy to Prevent Fraud and Scams, the Task Force lists [key components](https://fraudtaskforce.aspeninstitute.org/time-is-now) of a national strategy to include improved education of consumers to identify fraud, enhanced information sharing across industry, law enforcement, and regulatory agencies by use of data exchanges and legal mechanisms for sharing information. As well as empowering law enforcement with additional authority and resources. The document cites the recent [UK action](https://www.gov.uk/government/news/new-powers-to-seize-cryptoassets-used-by-criminals-go-live) as an example of recent amendments to law enforcement powers which in England means police will no longer be required to arrest seizing crypto from a suspect, can seize written passwords or memory sticks, as well as transfer "crypto assets" to a law enforcement wallet. In an August 2024 [interview](https://www.businessinsider.com/zelle-scams-how-to-get-money-back-2024-8?) with Fortune, Ben Chance, the Chief Fraud Risk Management Officer for Early Warning Services reportedly "told the outlet that the best way to prevent scams on money-sharing apps is better user education, sound policy and more funding for law enforcement." This sounds very similar to the National Strategy to Prevent Fraud and Scams being crafted by the National Task Force for Fraud & Scam Prevention, with more user education and law enforcement. No mention of standardized reimbursement policies or enhancing transparency around fraud investigations which are the primary accusations aimed at Zelle and its owners by the US Senate and the subject of the current investigation by the Consumer Financial Protection Bureau. @ d61f3bc5:0da6ef4a
2025-02-12 16:57:44Micropayments on the Internet have been theorized for decades. However, it wasn’t until the emergence of Nostr that we’ve finally seen them deployed at scale. Nostr is still in its infancy, yet we are already witnessing an explosion of apps built on top of this open protocol. And most of them are featuring zaps! With the recent Primal 2.1 release, Nostr developers now have the option to enhance the experience for their users by integrating a Nostr-powered bitcoin wallet. There is no doubt that micropayments add a new dimension to consumer apps. The incumbents have realized this and are rushing to add payments to their closed platforms. It won't be long before apps that don’t include built-in payments feel dated or outright broken. The question is not if apps of the future will have built-in payments, but what *kind* of payments they will be. Given that open networks have a tendency to win, our bet is that apps of the future will be powered by Bitcoin. Let’s see how Primal can help. ## Primal Wallet Our vision for Primal Wallet is simple: deliver the smoothest transactional bitcoin wallet, endowed with expert Nostr skills. The wallet leverages Nostr’s open social graph as a de facto public lightning directory, while offering the highest level of user experience for Nostr’s rich content. For example, the user can scroll through the transaction list, select a zap, and drill straight into the conversation thread where the zap originated. The whole flow feels perfectly natural.  Since we launched Primal Wallet in December 2023, the user response has been incredibly positive. People love the idea of being able to post something on Nostr, get zaps from plebs around the world, then buy a coffee or a meal with those sats - all from the same app. Having a bitcoin wallet with social skills resonated strongly with users, so Primal Wallet grew rapidly in popularity and usage. Since the launch, we have processed **1,338,460** transactions, with **238,916** just in the past month alone. This rivals some of the leading bitcoin wallets, and we are just getting started! We hear from many bitcoin OGs that they are using Primal Wallet as their transactional daily driver. Bullish. All this is great, but something has been missing. Our users demanded the ability to connect Primal Wallet to other Nostr apps, so they can zap from anywhere in Nostr’s growing ecosystem. ## Zapping from Any Nostr App For an existing Primal user, connecting the wallet to a new Nostr app can now be done in two clicks. Let’s take a look at how this is done from Olas, one of the most exciting new apps on Nostr:  Yes. Click, click. And you can start zapping! Such smooth integration of payments is not available in any competing technology stack. Tradfi, fintech, crypto, etc., have nothing on Bitcoin and Nostr. Two clicks and your external wallet is connected. I’ll give you a moment now to allow for this new reality to settle in. Primal enables you to connect any number of external apps and manage them from wallet settings:  Note that you can set your daily spend budget for each app or revoke its access at any time. ## How This Works So, what is this sorcery? How does it work under the hood? Connecting Nostr apps to external wallets is accomplished via the Nostr Wallet Connect protocol. It utilizes Nostr’s public relay infrastructure to enable communication between apps and wallets. You can learn more about this protocol [here](https://nwc.dev/), and access developer docs [here](https://docs.nwc.dev/). The smooth, two-click connection setup UX is implemented through deep links between Primal and the external app. Here’s the deep link that the external app needs to call to invoke this feature: ```nostrnwc+primal://connect?appicon=[icon_url]&appname=[app_name]&callback=[callback_string]``` After the user clicks “Create Wallet Connection” in Primal, the Primal app calls the deep link defined in the callback, and passes the NWC connection string. That's all that the external app needs to make the wallet connection. ## What Comes Next? The Nostr Wallet Connect protocol has been around for almost two years. Several bitcoin wallets implement it and many Nostr apps use it as their main way of enabling payments. What’s new with Primal 2.1 is the elevated user experience. Since Primal is a Nostr-powered wallet, it is aware of all the relevant metadata for each transaction: Nostr zaps, users, and the related events. Primal indexes the entire Nostr network, and now this is open to all Nostr apps that wish to integrate payments. Nostr keeps expanding and getting better. Its openness enables us to build capabilities that lift all boats. The future is bright; I can’t wait to see how things evolve from here. 🍿🍿🍿
@ d61f3bc5:0da6ef4a
2025-02-12 16:57:44Micropayments on the Internet have been theorized for decades. However, it wasn’t until the emergence of Nostr that we’ve finally seen them deployed at scale. Nostr is still in its infancy, yet we are already witnessing an explosion of apps built on top of this open protocol. And most of them are featuring zaps! With the recent Primal 2.1 release, Nostr developers now have the option to enhance the experience for their users by integrating a Nostr-powered bitcoin wallet. There is no doubt that micropayments add a new dimension to consumer apps. The incumbents have realized this and are rushing to add payments to their closed platforms. It won't be long before apps that don’t include built-in payments feel dated or outright broken. The question is not if apps of the future will have built-in payments, but what *kind* of payments they will be. Given that open networks have a tendency to win, our bet is that apps of the future will be powered by Bitcoin. Let’s see how Primal can help. ## Primal Wallet Our vision for Primal Wallet is simple: deliver the smoothest transactional bitcoin wallet, endowed with expert Nostr skills. The wallet leverages Nostr’s open social graph as a de facto public lightning directory, while offering the highest level of user experience for Nostr’s rich content. For example, the user can scroll through the transaction list, select a zap, and drill straight into the conversation thread where the zap originated. The whole flow feels perfectly natural.  Since we launched Primal Wallet in December 2023, the user response has been incredibly positive. People love the idea of being able to post something on Nostr, get zaps from plebs around the world, then buy a coffee or a meal with those sats - all from the same app. Having a bitcoin wallet with social skills resonated strongly with users, so Primal Wallet grew rapidly in popularity and usage. Since the launch, we have processed **1,338,460** transactions, with **238,916** just in the past month alone. This rivals some of the leading bitcoin wallets, and we are just getting started! We hear from many bitcoin OGs that they are using Primal Wallet as their transactional daily driver. Bullish. All this is great, but something has been missing. Our users demanded the ability to connect Primal Wallet to other Nostr apps, so they can zap from anywhere in Nostr’s growing ecosystem. ## Zapping from Any Nostr App For an existing Primal user, connecting the wallet to a new Nostr app can now be done in two clicks. Let’s take a look at how this is done from Olas, one of the most exciting new apps on Nostr:  Yes. Click, click. And you can start zapping! Such smooth integration of payments is not available in any competing technology stack. Tradfi, fintech, crypto, etc., have nothing on Bitcoin and Nostr. Two clicks and your external wallet is connected. I’ll give you a moment now to allow for this new reality to settle in. Primal enables you to connect any number of external apps and manage them from wallet settings:  Note that you can set your daily spend budget for each app or revoke its access at any time. ## How This Works So, what is this sorcery? How does it work under the hood? Connecting Nostr apps to external wallets is accomplished via the Nostr Wallet Connect protocol. It utilizes Nostr’s public relay infrastructure to enable communication between apps and wallets. You can learn more about this protocol [here](https://nwc.dev/), and access developer docs [here](https://docs.nwc.dev/). The smooth, two-click connection setup UX is implemented through deep links between Primal and the external app. Here’s the deep link that the external app needs to call to invoke this feature: ```nostrnwc+primal://connect?appicon=[icon_url]&appname=[app_name]&callback=[callback_string]``` After the user clicks “Create Wallet Connection” in Primal, the Primal app calls the deep link defined in the callback, and passes the NWC connection string. That's all that the external app needs to make the wallet connection. ## What Comes Next? The Nostr Wallet Connect protocol has been around for almost two years. Several bitcoin wallets implement it and many Nostr apps use it as their main way of enabling payments. What’s new with Primal 2.1 is the elevated user experience. Since Primal is a Nostr-powered wallet, it is aware of all the relevant metadata for each transaction: Nostr zaps, users, and the related events. Primal indexes the entire Nostr network, and now this is open to all Nostr apps that wish to integrate payments. Nostr keeps expanding and getting better. Its openness enables us to build capabilities that lift all boats. The future is bright; I can’t wait to see how things evolve from here. 🍿🍿🍿 @ 94a6a78a:0ddf320e
2025-02-12 15:05:48Azzamo is more than just a relay provider—it’s a **high-performance network** designed to make Nostr **faster, smoother, and more reliable** for everyone. Whether you're **posting notes, zapping sats, sharing media, or sending DMs**, Azzamo keeps your Nostr experience **seamless and efficient**. Nostr is unstoppable, but **not all relays are the same**. Some are **slow, unreliable, or disappear overnight**, while others get **overloaded**, making message delivery **inconsistent**. Azzamo is built differently—offering **fast, stable, and globally distributed relays** to ensure **low-latency, high-speed connections**, no matter where you are. --- ## **🌍 Premium Relays for Maximum Performance** Azzamo **Premium Relays** are optimized for **speed, reliability, and uptime**, available exclusively to **Premium users**: 📡 **Azzamo Premium Relays:** - **Europe:** `wss://relay.azzamo.net` - **America:** `wss://us.azzamo.net` - **Asia:** `wss://asia.azzamo.net` Add **Azzamo Premium Time** to **unlock unlimited, high-speed access** across these global relays. 🔗 **Get Premium:** [azzamo.net/premium](https://azzamo.net/premium) --- ## **🆓 Freemium Relays – Free for Everyone** Azzamo believes in **keeping Nostr open** and accessible to all. That’s why we offer **free relays for everyone**, with **no rate limits for Premium members** 📡 **Freemium Relays:** - **Free Relay:** `wss://nostr.azzamo.net` – Open to all. - **Inbox Relay:** `wss://inbox.azzamo.net` – Reliable for DMs & group messages. By offering both **free and premium options**, Azzamo ensures that **anyone can use Nostr, while also funding the infrastructure that keeps it running smoothly.** --- ## **🛡️ Minimal Moderation, Maximum Transparency** Nostr is about **free speech**, but that doesn’t mean **zero moderation.** Azzamo follows a **minimal moderation policy** to keep relays **functional and spam-free** while maintaining **transparency** in enforcement.\ \ 🚫 **Spam & network abuse**\ 🚫 **Illegal content (CSAM, fraud, malware, scams)**\ 🚫 **Impersonation & identity abuse** We also maintain a **public Ban API** for **transparent moderation decisions**. 📖 **More on our Ban API:** [azzamo.net/introducing-the-azzamo-ban-api](https://azzamo.net/introducing-the-azzamo-ban-api) --- ## **🚀 Get Started with Azzamo Relays Today!** 🔗 **Connect now:**\ 📡 `wss://nostr.azzamo.net` (Freemium Free Relay)\ 📬 `wss://inbox.azzamo.net` (Freemium Inbox Relay)\ 📡 `wss://relay.azzamo.net` (Premium Europe Relay)\ 📡 `wss://us.azzamo.net` (Premium Americas Relay)\ 📡 `wss://asia.azzamo.net` (Premium Asia Relay) Nostr is growing fast. **Make sure your relays can keep up.** 🚀 #azzamo #grownostr #nostr #relay #relays #premiumrelay #paidrelay
@ 94a6a78a:0ddf320e
2025-02-12 15:05:48Azzamo is more than just a relay provider—it’s a **high-performance network** designed to make Nostr **faster, smoother, and more reliable** for everyone. Whether you're **posting notes, zapping sats, sharing media, or sending DMs**, Azzamo keeps your Nostr experience **seamless and efficient**. Nostr is unstoppable, but **not all relays are the same**. Some are **slow, unreliable, or disappear overnight**, while others get **overloaded**, making message delivery **inconsistent**. Azzamo is built differently—offering **fast, stable, and globally distributed relays** to ensure **low-latency, high-speed connections**, no matter where you are. --- ## **🌍 Premium Relays for Maximum Performance** Azzamo **Premium Relays** are optimized for **speed, reliability, and uptime**, available exclusively to **Premium users**: 📡 **Azzamo Premium Relays:** - **Europe:** `wss://relay.azzamo.net` - **America:** `wss://us.azzamo.net` - **Asia:** `wss://asia.azzamo.net` Add **Azzamo Premium Time** to **unlock unlimited, high-speed access** across these global relays. 🔗 **Get Premium:** [azzamo.net/premium](https://azzamo.net/premium) --- ## **🆓 Freemium Relays – Free for Everyone** Azzamo believes in **keeping Nostr open** and accessible to all. That’s why we offer **free relays for everyone**, with **no rate limits for Premium members** 📡 **Freemium Relays:** - **Free Relay:** `wss://nostr.azzamo.net` – Open to all. - **Inbox Relay:** `wss://inbox.azzamo.net` – Reliable for DMs & group messages. By offering both **free and premium options**, Azzamo ensures that **anyone can use Nostr, while also funding the infrastructure that keeps it running smoothly.** --- ## **🛡️ Minimal Moderation, Maximum Transparency** Nostr is about **free speech**, but that doesn’t mean **zero moderation.** Azzamo follows a **minimal moderation policy** to keep relays **functional and spam-free** while maintaining **transparency** in enforcement.\ \ 🚫 **Spam & network abuse**\ 🚫 **Illegal content (CSAM, fraud, malware, scams)**\ 🚫 **Impersonation & identity abuse** We also maintain a **public Ban API** for **transparent moderation decisions**. 📖 **More on our Ban API:** [azzamo.net/introducing-the-azzamo-ban-api](https://azzamo.net/introducing-the-azzamo-ban-api) --- ## **🚀 Get Started with Azzamo Relays Today!** 🔗 **Connect now:**\ 📡 `wss://nostr.azzamo.net` (Freemium Free Relay)\ 📬 `wss://inbox.azzamo.net` (Freemium Inbox Relay)\ 📡 `wss://relay.azzamo.net` (Premium Europe Relay)\ 📡 `wss://us.azzamo.net` (Premium Americas Relay)\ 📡 `wss://asia.azzamo.net` (Premium Asia Relay) Nostr is growing fast. **Make sure your relays can keep up.** 🚀 #azzamo #grownostr #nostr #relay #relays #premiumrelay #paidrelay @ 3b7fc823:e194354f
2025-02-12 01:15:49We are constantly surrounded by technologies that claim to enhance our experiences but often come at the cost of our privacy. Think about it – every time you visit a website, cookies are being dropped like breadcrumbs, tracking your every move without you even knowing. **How Tech Companies Collect Your Data: The Spy Next Door** 1. **Cookies**: These tiny files are placed on your device as soon as you visit a site. They follow you around the web, creating a digital trail that companies use to learn about your habits and interests. 2. **Tracking Pixels**: Like cookies, these are invisible tags that track your actions across different websites. Imagine someone following you wherever you go online – that's what tracking pixels do. 3. **Behavioral Targeting**: This is when companies analyze your browsing history to serve you ads tailored to your interests. It's like knowing what you like and then bombarding you with it, whether you like it or not. 4. **Data Brokers**: These middlemen collect data from various sources and sell it on to the highest bidder. Your information could be used for marketing, insurance, or even political purposes – without your consent! 5. **Third-Party trackers**: Apps and websites you visit may share your data with other companies, creating a web of surveillance that's hard to escape. **What They Do with Your Data** Once companies have your data, they can use it for targeted advertising, profile building, and even political manipulation. Think about the Cambridge Analytica scandal... Your data isn't just used to make your experience better; it's being sold and exploited in ways you probably never imagined. **How to Stop Them: Empower Yourself** 1. **Use Privacy-Friendly Browsers**: Tools like Brave or Firefox with enhanced tracking protection can block trackers and cookies, giving you control over what data is collected. 2. **Block Trackers and Cookies**: Browser extensions that allow you to block these elements are available for free, providing an added layer of privacy. 3. **Minimize Data Usage**: When using apps or websites, avoid granting unnecessary permissions that could lead to data collection. 4. **Delete Unused Apps**: Regularly delete apps and services that are no longer needed to stop data collection from inactive accounts. 5. **Read Privacy Policies**: Before accepting terms of service or privacy policies, read through them to understand what data will be collected and how it will be used. 6. **Use Incognito or Private Browsing Modes**: These modes often block cookies and trackers, offering an additional way to reduce data collection. But remember that Google was still tracking you on Chrome regardless, so your mileage may vary. 7. **Limit Device Usage**: Avoid using personal devices for sensitive activities when privacy is a concern. 8. **Use Tor**: Yes it's slower, yes some sites won't work. It's more private and you using helps disquise traffic giving protection for others that might need it more than you do. **Why It Matters: The Domino Effect** The data collected today isn't just for ads; it's used in decision-making processes that can affect your life. From insurance rates to job opportunities, your data can influence significant aspects of your existence. Imagine a world where your information is bought and sold without your consent – it's time to take control. **Your Data, Your Choice** Your data is being collected and sold without your consent, and the time to act is now. By understanding how data collection works and taking steps to protect yourself, you can reclaim control over your privacy. Remember, you're not just a user – you're the owner of your information. It's time to stand up for your rights and demand transparency from the companies that claim to serve you. **Don't Let Corporate Spies Steal Your Privacy** Your data is valuable, and it's being harvested without your knowledge. Take action today by educating yourself and others about the importance of privacy. Together, we can create a world where privacy is respected and protected, not exploited for profit. Join the movement to fight against corporate surveillance and protect your right to privacy. Your information is too important to leave in the hands of those who don't have your consent. It's time to take a stand – your digital life depends on it. --- Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero 82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
@ 3b7fc823:e194354f
2025-02-12 01:15:49We are constantly surrounded by technologies that claim to enhance our experiences but often come at the cost of our privacy. Think about it – every time you visit a website, cookies are being dropped like breadcrumbs, tracking your every move without you even knowing. **How Tech Companies Collect Your Data: The Spy Next Door** 1. **Cookies**: These tiny files are placed on your device as soon as you visit a site. They follow you around the web, creating a digital trail that companies use to learn about your habits and interests. 2. **Tracking Pixels**: Like cookies, these are invisible tags that track your actions across different websites. Imagine someone following you wherever you go online – that's what tracking pixels do. 3. **Behavioral Targeting**: This is when companies analyze your browsing history to serve you ads tailored to your interests. It's like knowing what you like and then bombarding you with it, whether you like it or not. 4. **Data Brokers**: These middlemen collect data from various sources and sell it on to the highest bidder. Your information could be used for marketing, insurance, or even political purposes – without your consent! 5. **Third-Party trackers**: Apps and websites you visit may share your data with other companies, creating a web of surveillance that's hard to escape. **What They Do with Your Data** Once companies have your data, they can use it for targeted advertising, profile building, and even political manipulation. Think about the Cambridge Analytica scandal... Your data isn't just used to make your experience better; it's being sold and exploited in ways you probably never imagined. **How to Stop Them: Empower Yourself** 1. **Use Privacy-Friendly Browsers**: Tools like Brave or Firefox with enhanced tracking protection can block trackers and cookies, giving you control over what data is collected. 2. **Block Trackers and Cookies**: Browser extensions that allow you to block these elements are available for free, providing an added layer of privacy. 3. **Minimize Data Usage**: When using apps or websites, avoid granting unnecessary permissions that could lead to data collection. 4. **Delete Unused Apps**: Regularly delete apps and services that are no longer needed to stop data collection from inactive accounts. 5. **Read Privacy Policies**: Before accepting terms of service or privacy policies, read through them to understand what data will be collected and how it will be used. 6. **Use Incognito or Private Browsing Modes**: These modes often block cookies and trackers, offering an additional way to reduce data collection. But remember that Google was still tracking you on Chrome regardless, so your mileage may vary. 7. **Limit Device Usage**: Avoid using personal devices for sensitive activities when privacy is a concern. 8. **Use Tor**: Yes it's slower, yes some sites won't work. It's more private and you using helps disquise traffic giving protection for others that might need it more than you do. **Why It Matters: The Domino Effect** The data collected today isn't just for ads; it's used in decision-making processes that can affect your life. From insurance rates to job opportunities, your data can influence significant aspects of your existence. Imagine a world where your information is bought and sold without your consent – it's time to take control. **Your Data, Your Choice** Your data is being collected and sold without your consent, and the time to act is now. By understanding how data collection works and taking steps to protect yourself, you can reclaim control over your privacy. Remember, you're not just a user – you're the owner of your information. It's time to stand up for your rights and demand transparency from the companies that claim to serve you. **Don't Let Corporate Spies Steal Your Privacy** Your data is valuable, and it's being harvested without your knowledge. Take action today by educating yourself and others about the importance of privacy. Together, we can create a world where privacy is respected and protected, not exploited for profit. Join the movement to fight against corporate surveillance and protect your right to privacy. Your information is too important to leave in the hands of those who don't have your consent. It's time to take a stand – your digital life depends on it. --- Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero 82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1 @ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content. ## Key Features: ### Video Processing: - Automatically downloads YouTube videos, transcripts, and chapter information - Splits transcripts into sections based on video chapters ### Content Summarization: - Utilizes language models to transform spoken content into clear, readable text - Formats output in AsciiDoc for improved readability and navigation - Highlights key terms and concepts with [[term]] notation for potential cross-referencing ### Diagram Extraction: - Analyzes video entropy to identify static diagram/slide sections - Provides a user-friendly GUI for manual selection of relevant time ranges - Allows users to pick representative frames from selected ranges ## Going Forward: Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care. While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs. ## Screenshots ### Frame Selection  This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection. ### Diagram Extraction  This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save. ## Links - repo: https://github.com/limina1/video_article_converter - Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE ## Output And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101 Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
@ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content. ## Key Features: ### Video Processing: - Automatically downloads YouTube videos, transcripts, and chapter information - Splits transcripts into sections based on video chapters ### Content Summarization: - Utilizes language models to transform spoken content into clear, readable text - Formats output in AsciiDoc for improved readability and navigation - Highlights key terms and concepts with [[term]] notation for potential cross-referencing ### Diagram Extraction: - Analyzes video entropy to identify static diagram/slide sections - Provides a user-friendly GUI for manual selection of relevant time ranges - Allows users to pick representative frames from selected ranges ## Going Forward: Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care. While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs. ## Screenshots ### Frame Selection  This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection. ### Diagram Extraction  This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save. ## Links - repo: https://github.com/limina1/video_article_converter - Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE ## Output And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101 Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3 @ 916a7ab7:146bb83e
2025-02-04 13:35:11It was not ago that my life was simpler than it is today. I remember being a simple clone, droning on through a structured life as I'd been trained to do since birth. Like most people I knew, I was raised in a world where you were mentally prepared for a conceptually simple life: 1. Finish high school, if possible. 2. Go to college, if possible. 3. Find a job. 4. Earn money. 5. Pay bills. 6. Get married. 7. Start a family. 8. Pay more bills. 9. Raise family and (hopefully) launch the kids. 10. Plan to retire, but expect to work into your 70s. It was a programmed formula for life. A generational blueprint, if you will. Sure, there would be unpredictable details, but I expected my life to follow this path. As I plodded along through my fairly boring life, I checked most of those things off the list. High school was easy, but getting off the farm was not. Enlisting in the military solved that problem, and the pay in the mid-1990s wasn't bad for a 17 year old kid with no bills. I got paid every two weeks, lived in the barracks, and spent most of my money on booze. Life was good, and I had no other purpose than to do my job and keep earning money. Before I knew it, though, everything changed. I got married, had some kids and accumulated a mountain of debt. Like my parents before me, I was stuck in a never ending cycle of working my ass off, paying bills, buying food, and trying to save what little money was left over for a future that was unpredictable at best. Financial struggles stressed our marriage, the kids continued eating more and more food, and then 2008 tanked the value of our home. That was the first nudge that stirred my oblivious slumber. And there was more to come. Rising taxes, inflation, the clown show at the federal reserve, the wars funded by central banks, an astronomical national debt, and the burdens of our mistakes weighing down the futures of our children. Not to mention a federal government that actively seeks to censor, suppress, and financially imprison its own people. The times exuded chaos. Then a few months ago, I woke up... It happened during an episode of The Tuttle Twins, a cartoon show from Angel Studios. I homeschool my three youngest kids, and I'd let them watch TV during lunch so I could grade some papers. This cartoon was new to me, but the kids liked the music and the crazy raccoon. As fate would have it, they ended up watching an episode about Bitcoin. This, of course, led to a long series of questions: "Dad, what's Bitcoin?" "Is Bitcoin real?" "Do you have Bitcoin?" "Can I get Bitcoin for allowance instead of dollars?" I had no answers for these questions, so we started doing some research together. We turned on our Chromebooks and launched a barrage of web searches. After reading a bunch of articles I came away with the idea that Bitcoin might be a real thing. Later that evening, and after the kids were in bed, I couldn't stop thinking about Bitcoin. I honestly didn't understand half of what I read in those articles, which bothered me. I'm not a super smart guy, but I catch on to things pretty quickly, and I wanted to better understand what I'd read. I expanded my search to podcasts and YouTube videos. I ended up listening to a couple episodes from a Bitcoin Veterans podcast. As a veteran myself, I figured that this group of Bitcoin-savvy veterans would be able to help me figure out all this madness. I was right. I quickly learned that the word "Bitcoin" was just the tip of the iceberg, and I quickly found myself falling through an endless rabbit hole. They pointed me in a lot of different directions, but they were all helpful. (If you're a US military veteran and want to connect with this group, find them at [bitcoinveterans.org].) A couple months ago, I couldn't tell you the difference between a Bitcoin and a meme coin. I'd come across the phrase Bitcoin mining, and I just thought there was a special group of people who mined a special metal to create coins with a big "B" on them. Why couldn't they just use the metal we already mined? Sheesh! I thought nostr was a virus, and a Kraken was still a giant squid. As of today, I'm happy to say that I've made a little bit of progress. Those things above no longer confuse me, and I actually have a little bit of Bitcoin now. Sure, I'm still trying to wrap my head around NFTs and figure out who the Pepe frog man is, but I'm no longer completely lost. Not to mention, I just spent most of the last 24 hours figuring this whole nostr thing out, which excites me. I kind of missed the boat on the big name social media platforms, so I'm looking forward to this new decentralized approach to things. For now, I'm just happy to be awake. Finally. I see the need for decentralization and the necessity of moving away from fiat monies. I don't have much to offer except my intellect and my love of writing, but I'm here to serve in any way that I can.
@ 916a7ab7:146bb83e
2025-02-04 13:35:11It was not ago that my life was simpler than it is today. I remember being a simple clone, droning on through a structured life as I'd been trained to do since birth. Like most people I knew, I was raised in a world where you were mentally prepared for a conceptually simple life: 1. Finish high school, if possible. 2. Go to college, if possible. 3. Find a job. 4. Earn money. 5. Pay bills. 6. Get married. 7. Start a family. 8. Pay more bills. 9. Raise family and (hopefully) launch the kids. 10. Plan to retire, but expect to work into your 70s. It was a programmed formula for life. A generational blueprint, if you will. Sure, there would be unpredictable details, but I expected my life to follow this path. As I plodded along through my fairly boring life, I checked most of those things off the list. High school was easy, but getting off the farm was not. Enlisting in the military solved that problem, and the pay in the mid-1990s wasn't bad for a 17 year old kid with no bills. I got paid every two weeks, lived in the barracks, and spent most of my money on booze. Life was good, and I had no other purpose than to do my job and keep earning money. Before I knew it, though, everything changed. I got married, had some kids and accumulated a mountain of debt. Like my parents before me, I was stuck in a never ending cycle of working my ass off, paying bills, buying food, and trying to save what little money was left over for a future that was unpredictable at best. Financial struggles stressed our marriage, the kids continued eating more and more food, and then 2008 tanked the value of our home. That was the first nudge that stirred my oblivious slumber. And there was more to come. Rising taxes, inflation, the clown show at the federal reserve, the wars funded by central banks, an astronomical national debt, and the burdens of our mistakes weighing down the futures of our children. Not to mention a federal government that actively seeks to censor, suppress, and financially imprison its own people. The times exuded chaos. Then a few months ago, I woke up... It happened during an episode of The Tuttle Twins, a cartoon show from Angel Studios. I homeschool my three youngest kids, and I'd let them watch TV during lunch so I could grade some papers. This cartoon was new to me, but the kids liked the music and the crazy raccoon. As fate would have it, they ended up watching an episode about Bitcoin. This, of course, led to a long series of questions: "Dad, what's Bitcoin?" "Is Bitcoin real?" "Do you have Bitcoin?" "Can I get Bitcoin for allowance instead of dollars?" I had no answers for these questions, so we started doing some research together. We turned on our Chromebooks and launched a barrage of web searches. After reading a bunch of articles I came away with the idea that Bitcoin might be a real thing. Later that evening, and after the kids were in bed, I couldn't stop thinking about Bitcoin. I honestly didn't understand half of what I read in those articles, which bothered me. I'm not a super smart guy, but I catch on to things pretty quickly, and I wanted to better understand what I'd read. I expanded my search to podcasts and YouTube videos. I ended up listening to a couple episodes from a Bitcoin Veterans podcast. As a veteran myself, I figured that this group of Bitcoin-savvy veterans would be able to help me figure out all this madness. I was right. I quickly learned that the word "Bitcoin" was just the tip of the iceberg, and I quickly found myself falling through an endless rabbit hole. They pointed me in a lot of different directions, but they were all helpful. (If you're a US military veteran and want to connect with this group, find them at [bitcoinveterans.org].) A couple months ago, I couldn't tell you the difference between a Bitcoin and a meme coin. I'd come across the phrase Bitcoin mining, and I just thought there was a special group of people who mined a special metal to create coins with a big "B" on them. Why couldn't they just use the metal we already mined? Sheesh! I thought nostr was a virus, and a Kraken was still a giant squid. As of today, I'm happy to say that I've made a little bit of progress. Those things above no longer confuse me, and I actually have a little bit of Bitcoin now. Sure, I'm still trying to wrap my head around NFTs and figure out who the Pepe frog man is, but I'm no longer completely lost. Not to mention, I just spent most of the last 24 hours figuring this whole nostr thing out, which excites me. I kind of missed the boat on the big name social media platforms, so I'm looking forward to this new decentralized approach to things. For now, I'm just happy to be awake. Finally. I see the need for decentralization and the necessity of moving away from fiat monies. I don't have much to offer except my intellect and my love of writing, but I'm here to serve in any way that I can.