-

@ da0b9bc3:4e30a4a9
2025-04-03 07:02:17
Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/933122
-

@ 0f9da413:01bd07d7
2025-04-03 05:32:55

หลังจากจบทริปเที่ยวพัทยาเรียบร้อยแล้วก็ได้เดินทางไปยังเกาะช้างโดยติดรถเจ้าหน้าที่ในที่ทำงานไปไปเกาะช้างครั้งแรกรู้สึกว่ามันไกลเหลือเกินไปค่อนข้างยากหากไม่มีรถส่วนตัว ถ้าให้ไปส่วนตัวก็คงต้องอยู่นานๆ หน่อยชักแบบอาทิตย์หนึ่ง ใช้ชีวิตแบบฝรั่งเที่ยวอยู่ง่ายๆ กินง่ายๆ จากที่ดูในแผนที่ btcmap แล้วพบว่าก็มีร้านที่ปักหมุดไว้อยู่ทั้งหมดสองร้านด้วยกันซึ่งระยะทางก็ค่อนข้างซันเหมือนกัน และมีเนินสูงต่ำสลับกันไป หากไม่มีรถส่วนตัวไปนี่ค่อนข้่างลำบากพอสมควร ต้องเช่ามอไซต์ไป อันนี้ก็เช่าไปเหมือนกัน โดยผมเช่ามอไซต์ 1 วันวันละ 200 บาท (แต่มัดจำ 3000 บาท) ก็เอาเรื่องเหมือนกัน และก็มาเริ่มต้นที่ร้านแรกเลยคือ
---
### **Mr. A Coffee**

ร้านอาหารสไตล์บ้านๆ ที่ขายอาหาร น้ำ เครื่องดื่ม มีทั้งอาหารไทยและอาหารฝรั่ง ส่วนตัวก็ขับรถมอไซต์มายังสถานที่แห่งนี้ทางเข้าไปยังร้านเป็นหมู่บ้านเล็กๆ ไม่มีถนนเข้า แต่มอไซต์เข้าไปได้พอสมควร ตอนนั้นค่อนข้างเย็นมากแล้ว ได้มาสั่งอาหารมาคือ ข้าวเหนียวมะม่วงกับน้ำแก้วมังกรปั่นแบบไม่หวาน (ทั้งๆที่ตัวเองก็จะเตรียมไปกินบุ๊ปเฟ่อีกหนึ่งชั่วโมงข้างหน้า 555) ก็ได้สั่งไปแล้วก็ถามว่ารับ bitcoin ไหมครับ เจ้าของร้านก็บอกว่า รับๆ ผมกับเจ้าของร้านก็ได้พูดคุยกันเกือบประมาณครึ่งชั่วโมง ซึ่งหากผมมาเร็วกว่านี้หน่อยก็คงได้คุยกันยาวๆ แล้วละ ซึ่งเป็นการคุยที่สนุกมากซึ่งตัวเจ้าของร้านเองก็ได้เล่าถึงเหตุผลที่รับ bitcoin เหมือนกันว่าช่วง โควิดตอนปี 2020 ที่ผ่านมา บนเกาะช้างไม่มีอะไรเลยชาวบ้านก็ต้องไปหารากไม้ หาเห็ดตามป่าเขากัน แต่พี่เจ้าของร้านได้รู้จักกับฝรั่งคนหนึ่งเขาช่วยเหลือพี่เจ้าของร้านด้วยการบริจาคบิทคอยให้ และคนนี้ก็เป็นคนสอนให้เขารับบิทคอยโดยใช้ WOS และเจ้าของร้านก็เล่าให้ผมฟังเพิ่มเติม ณ ปัจจุบันว่า คนเราเองก็ยังต้องมีสภาพคล่องในการใช้งานอยู่ ตั้งมีเงิน fiat ไว้ส่วนหนึ่ง ส่วนบิทคอยที่ได้เขาได้ก็เก็บไว้เพื่อสร้างเป็นทรัพย์สินในอนาคตที่หากมีปัญหาช่วงไหนก็นำมาขายได้ ก็แลก P2P โดยตรง ซึ่งผมค่อนข้างตกใจเพราะเขาเรียนรู้จากการรับบิทคอยโดยนักท่องเที่ยวชาวต่างชาติที่ชวนเขาให้รับ เผื่อว่าจะมีฝรั่งมาใช้งานบิทคอย ณ สถานที่ร้านแห่งนี้

กึมมิคที่หลายท่านอาจจะต้องลุ้นหน่อยว่าหากมีโอกาสได้ไปเที่ยวและแวะที่ร้าน ก็คงต้่องลุ้นว่าคุณจะได้จ่ายด้วย bitcoin ไหม หากวันนั้นเจ้าของร้านไม่อยากรับเพราะว่าโคต้ารับบิทคอยวันนั้นเต็มแล้ว ฮ่าๆ รูปแบบระบบวาสนาร้านสูญของคุณมิกตอนเมื่อก่อน (เหมือนกันเลย) จริงๆ แล้วหากมีเวลามากพอก็คงได้พูดคุยกับพี่เจ้าของร้านสนุกๆกันไป ผมชอบความเรียบง่ายของร้านพี่เขา และมีอาหารหลากหลายอย่างเต็มไปหมด อีกเรื่องอย่างข้าวเหนียวมะม่วง ผมยังจำได้ว่าเมื่อก่อนมีแต่ช่วงฤดูเดียวที่สามารถกินมะม่วงสุกได้ หรือ อาหารแบบข้าวเหนียวมะม่วง แต่ปัจจุบันคือถ้าจะกิน ข้าวเหนียวมะม่วงแล้ว สามารถสั่งกินได้ตลอดทั้งปีกันเลยซึ่งก็โอเครพอสมควร แบบอยากไปทะเลตอนหน้าฝนแล้วอยากกินข้าวเหนียวมะม่วงของหน้าร้อนแบบนี้

ท้ายสุดร้าน Mr. A Coffee เป็นร้านที่ถ้านั่งชิวๆ แบบฝรั่งก็สามารถอยู่ได้ยาวๆ เลยนะจิบกาแฟ ทำงาน WFH ล้่อมรอบโดยธรรมชาติ แต่เส้นทางมาที่ร้านก็ลำบากหน่อยเหมาะกับคนที่ local จริงๆ low time ระดับหนึ่ง ท้ายสุดผมเองก็แจกสติกเกอร์ของพี่แชมป์เอาไปให้เจ้าของร้านแจกกันต่อไป

งานนี้ทั้งข้าวเหนียวมะม่วงและน้ำแก้วมังกรปั่น เสีย sats ไปทั้งหมด 6,050 sats แต่สิ่งที่ได้คือการแลกเปลี่ยนมุมมองกับเจ้าของร้านกับจุดเริ่มต้นของการรับบิทคอยในพื้นที่เกาะช้างแห่งนี้ และหากมีโอกาสอาจจะไปพักอยู่แถวนั้นชักอาทิตย์และแวะมาอุดหนุนร้านนี้ตลอด เพราะวิวฝั่งใต้สุดของเกาะช้างก็ยังคงความสวยงามไม่แพ้กับฝั่งทิศตะวันตกที่ฝรั่งอยู่กัน แต่ฝั่งใต้โซนนี้ก็มีความที่เป็นบ้านไม้ เพิงง่ายๆ ที่ชาวต่างชาติชอบกันอยู่ :)
Google-map: https://maps.app.goo.gl/b45JGeTzL6Lwwi9i9
BTC-map: https://btcmap.org/merchant/node:12416107504
---
### **Koh Chang Wine Gallery **

และเราก็ย้อนกลับมาอีกร้านหนึ่งในวันถัดไปและเป็นวันที่จะต้องออกจากเกาะช้างเช่นเดียวกัน และผมก็ไม่พลาดร้าน Koh Chang Wine Gallery ตั้งอยู่ในโซนหมู่บ้านแหล่งท่องเที่ยวเส้นทางถนนทางตะวันตก ร้านนี้ไม่ได้มีป้ายรับบิทคอย แต่รับชำระด้วยบิทคอยซึ่งเป็นฝรั่งท่านหนึ่งที่คาดว่าน่าจะแต่งงานกับภรรยาคนไทย เป็นร้านสไตล์แบบฝรั่งเลย ผมเองก็สั่งสเต็กเนื้อไป และน้ำมะม่วงปั่น (ไม่รู้เวลาไปเกาะทีไรติดใจกับน้ำมะม่วงปั่น) อาจจะไม่ได้พูดคุยอะไรมากมายนัก แต่ก็หมดไป 32,620 sats เป็นร้านอาหารเช้าและอาหารแนวฝรั่งตรงๆ ถือว่าค่อนข้างอร่อยใช้ได้ดีเลยทีเดียว แต่หากจะจ่ายด้วยบิทคอยก็ต้องแจ้งก่อนนะว่าขอจ่ายด้วยบิทคอยก่อน เหมือนพี่ฝรั่งที่เขารับตอนนี้ก็รับแต่เฉพาะ bitcoin อย่างเดียวเมื่อก่อนรับ xrp กับ doge ด้วยแต่ผมเองเวลาคุยกับฝรั่งก็เหงื่อแตกเหมือนกัน (รึว่าเพราะมันร้อน บนเกาะก็อบอ้าวใช้ได้ 555+)



Google-map: https://maps.app.goo.gl/6QbNgRbiV5Uao2Xz8
BTC-map: https://btcmap.org/merchant/node:11461720813
---
เส้นทางไปร้านค่อนข้างง่ายติดถนนในหมู่บ้าน ซึ่งหากมายังเกาะช้างแล้วหากขึ้นฝั่งมาแล้วเลี้ยวขวาก็จะขับรถหรือนั่งรถมาเส้นถนนฝั่งตะวันตกของเกาะก็จะพบกับร้านนี้ก่อน อันนี้แล้วแต่ความสะดวกแต่ละท่านเลยครับหากได้มีโอกาสแวะมาเกาะช้างและอยากใช้จ่าย bitcoin เราก็มีทางเลือกร้านในสองสไตล์กันเลย แบบวิถีฝรั่งตอนเช้าก็ร้าน Koh Chang Wine Gallery หรือ แบบ Local ก็ Mr. A Coffee หรือไปทังคู่เลยจะดีมากแต่ต้องบ้าหน่อย เพราะเส้นทางไปก็ค่อนข้างลำบากพอควรเหมือนกัน หมายถึงมีภูเขาชันมีทางขึ้นลงหักศอกนิดหน่อยก็เท่านั้นเอง
รวมๆ ทริปบนเกาะช้างนี้ก็หมดไปไม่เยอะมาก 38,670 sats ก็จะตัวลอยเบาๆ หน่อย (สำรวจเมื่อ มีนาคม 2025 อนาคตอาจจะมีการเปลี่ยนแปลงได้) สำหรับจากนี้จะเป็นการ ปสก. ส่วนตัวกับการใช้งาน Bitcoin Lightning ตามสถานที่ที่ได้เดินทาง Part 3 จะเป็นสถานที่ในพื้นที่หาดใหญ่ จังหวัดสงขลา และ เสริมประสบการณ์การเดินทางโดยรถไฟระยะเวลาเกือบ 18 ชั่วโมง พร้อมด้วยมิตรสหายในรังอย่างกัปตัน จะป่วนแค่ไหนก็รอติดตามกันครับ :)
-

@ d5c3d063:4d1159b3
2025-04-03 04:09:56
### ทรัมป์ ขึ้นภาษีนำเข้า
สิ่งที่คุณเห็น…กับสิ่งที่คุณมองไม่เห็น
คุณ #เห็น แค่ฝั่งที่ดูดีในข่าวภาคค่ำ
แต่คุณ #ไม่เห็น
– คนทั้งประเทศ ต้องจ่ายของแพงขึ้น
– ธุรกิจเล็ก ๆ ที่พึ่งการนำเข้า…ถูกบีบให้ตาย
– ผู้บริโภคต้องเสียเงินมากขึ้น โดยไม่มีทางเลือก
รัฐอ้างว่า *"ปกป้องประเทศ"* แต่จริง ๆ แล้วเขาแค่
โยนภาระให้คนส่วนใหญ่ เพื่ออุ้มผลประโยชน์บางกลุ่ม
เหมือนที่ Bastiat เรียกว่า *“การปล้นที่ถูกกฎหมาย”*
Hazlitt ขยายต่อใน Economics in One Lesson ว่า
> เศรษฐศาสตร์ที่ดี ต้องมองให้พ้นจากผลเฉพาะหน้า
> และมองให้เห็นผลกระทบต่อทุกคน ไม่ใช่แค่บางกลุ่ม
เงินเฟ้อ คือการขโมยแบบเงียบ ๆ
ภาษีศุลกากร คือการปล้นอย่างเปิดเผย
วันนี้ #EIOL น่าจะถึงมือเพื่อนๆ หลายคนแล้ว เล่มนี้ไม่ต้องอ่านทีละบทก็ได้ ลองเปิดไปบทที่ 11 เลยแล้วจะเจอ**ค้อนปอน**สำหรับทุบมายาคดีทางเศรษฐกิจที่รัฐใช้กับเรามาทั้งชีวิต
อ่าน #เศรษฐศาสตร์เล่มเดียวจบ แล้วคุณอาจไม่มีวันมอง “นโยบายเพื่อประชาชน” ได้เหมือนเดิมอีก เพราะบางที...สิ่งที่คุณไม่เคยเห็น อาจเป็นสิ่งที่คุณควรรู้(เห็น)ให้เร็วที่สุด
#Siamstr
-

@ 378562cd:a6fc6773
2025-04-02 22:41:57
Nostr is a decentralized, censorship-resistant social media protocol designed to give users control over online interactions without relying on central authorities. While its architecture offers notable advantages, it also introduces challenges, particularly concerning user anonymity, content moderation, and the dynamics of user influence.
Anonymity and the Risk of Bullying
Nostr's design allows users to create identities without traditional verification methods like email addresses or phone numbers. Instead, users generate a cryptographic key pair: a public key serving as their identifier and a private key for signing messages. This approach enhances privacy but can lead to the "online disinhibition effect," where individuals feel less accountable for their actions due to perceived anonymity. This phenomenon has been linked to increased instances of cyberbullying, as users may engage in behavior online that they would avoid in face-to-face interactions.
Influence Disparities Among Users
In decentralized networks like Nostr, users with larger followings can have a more extensive reach, amplifying their messages across the network. This can create disparities where individuals with thousands of followers wield more influence than those with fewer connections. While this dynamic is not unique to Nostr, the protocol's structure may exacerbate the visibility gap between highly followed users and those with a smaller audience.
Content Moderation and the Challenge of Deletion
Due to Nostr's decentralized nature, content moderation and deletion present significant challenges. Removing content to multiple relays becomes complex once a user posts content to multiple relays, as each relay operates independently. Unlike centralized platforms where a post can be deleted universally, Nostr's architecture means that deleting a post from one relay doesn't ensure its removal from others. This persistence underscores the importance of thoughtful posting, as content may remain accessible indefinitely.
Mitigation Strategies and User Empowerment
Despite these challenges, Nostr offers mechanisms to empower users to manage their experience. Clients can implement features allowing users to mute or block others, tailoring their interactions and content exposure. Additionally, some clients support user-led moderation, enabling individuals to label content as offensive or inappropriate, contributing to a community-driven approach to content management.
In summary, while Nostr's decentralized and anonymous framework promotes freedom and resistance to censorship, it also necessitates a proactive approach from users to navigate challenges related to anonymity, influence disparities, and content permanence. As the platform evolves, ongoing development and community engagement will be crucial in addressing these issues to foster a safe and equitable environment for all participants.
-

@ 3c7dc2c5:805642a8
2025-04-02 21:15:55
## 🧠Quote(s) of the week:
CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs.
## 🧡Bitcoin news🧡
2025
https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg
On the 24th of March:
➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity.
➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion).
Look at the corporate Bitcoin ownership breakdown:
- MicroStrategy: 506,000+ BTC
- Marathon: ~46,000 BTC (10x smaller)
- Riot: ~19,000 BTC (26x smaller)
That acquisition curve has gone parabolic since Q4 2024.
Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale.
Clear institutional conviction signal here.' -Ecoinometrics
➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine."
On the 25th of March:
➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL
- This is one of the most reliable "buy" indicators.
- Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive
(foto)
Bitcoin is always a buy. Just DCA.
➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest.
➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin.
➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o
Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world.
Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives)
But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.'
➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization".
I rather believe the opposite.
Under Femke Halsema - Amsterdam
- The number of civil servants increased by 50% (14K -> 20K)
- Debt increased by 150% (4 billion -> approx. 10 billion)
Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity.
Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better.
➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment.
➡️BlackRock launched a European Bitcoin ETP today - Bloomberg
➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin.
On the 26th of March:
➡️NYDIG just became a big Bitcoin miner.
Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG.
➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds.
➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest.
That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds.
➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses.
➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD.
→ Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin
→ Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin
→ Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet
This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time.
Source: https://t.co/QDj61ZDe6O
The Blockchain Group is Europe's First Bitcoin Treasury Company!
On the 27th of March:
➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard
➡️Daniel Batten: Yet another paper on Bitcoin and energy
TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition
are greater than generally assumed"
The journal has a (high) impact factor of 7.1."
Source: https://t.co/W3gytMgcpC
➡️A home miner with only 4 machines mined block 888737.
https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg
Bitcoin proves anyone can participate and earn—true freedom!
➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks.
200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News
➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025.
On the 28th of March:
➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today.
ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes!
➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina.
➡️A Russian company built a Bitcoin mine in the Arctic.
Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs.
➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity.
https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg
another great chart:
https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg
On the 29th of March:
➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin.
https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png
➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill.
If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use.
➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207.
On the 31st of March:
➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders:
“If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin."
https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf
➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin.
➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds.
➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem.
A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia.
Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening.
https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg
On the 1st of April:
➡️'Over 73,353 BTC were bought by corporations in Q1 2025.
Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now...
Which company do you want to see adopt BTC next?'
Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723
➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC.
On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC.
➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish
➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county.
➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide.
Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.'
## 💸Traditional Finance / Macro:
On the 29th of March
👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION.
Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL
## 🏦Banks:
👉🏽 no news
## 🌎Macro/Geopolitics:
On the 24th of March:
👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history.
Every time it crossed this level it marked the beginning of an 18-month recession/depression.
1929, 1973, 2008 & 2025'
I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both.
👉🏽US household wealth is falling:
US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates.
By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion.
In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback.
Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks.
This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures.
Consumer spending is set to slow in Q2 2025.' -TKL
👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes.
BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left."
Today, the 27th of March, marks those 1,028 days, and nothing happened.
Climate doomers are like Aztecs who think the sun stops unless they cut out some organs."
👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today.
For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/
They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe.
On the 25th of March:
👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though.
👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse.
The Green Deal is moving full speed ahead—soon everyone will be relying on food banks…
For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen
On the 26th of March:
👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all.
Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening.
On the 27th of March:
👉🏽Gold surpasses $3,100 for the first time in history.
TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years.
This is also the 3rd-longest streak on record after a historic run during the late 1970s.
The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation.
As a result, gold prices recorded 4 consecutive yearly gains.'
On the 31st of March for the first time, gold blasted through $100,000/kilogram.
This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.'
👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come.
On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored."
On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over."
That is the Mark I know!
"Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.”
On the 28th of March:
👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993.
Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed.
Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction.
It’s negative even “gold adjusted”
4 weeks ago it was +2.3%
8 weeks ago it was +3.9%
Yikes!
👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure.
The remaining 900 employees are set to be terminated.
👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei
👉🏽Fix the money, fix the world:
DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government”
“It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account”
“We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION”
“There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit”
Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe.
On the 29th of March:
👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion.
Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge
On the 1st of April:
In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week:
https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg
APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros.
Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!?
For our own housing market? “Too political.”
For war and Brussels' military ambitions? €100,000,000,000—no problem.
They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda.
Got Bitcoin?
I will end this Weekly Recap with a Stanley Druckenmiller quote:
"My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully."
"I tend to think that's what great investors do."
I know what I do and have. Bitcoin!
## 🎁If you have made it this far I would like to give you a little gift:
What Bitcoin Did:
Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy.
https://www.youtube.com/watch?v=_bSprc0IAow
Credit: I have used multiple sources!
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly.
`Use the code SE3997`
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀
⠀
⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you? If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-

@ ef53426a:7e988851
2025-04-02 21:02:06
# Bartering and early money
\
Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align.
Enter money. It’s used as an indirect exchange for any goods, so everyone wants it.
Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services.
As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money.
---
# Gold — the basis for sound money
\
Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining).
Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something.
Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money.
---
# Currencies devalued
\
Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire.
The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold.
In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned.
---
# Government-backed money
\
Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies.
By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate.
The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold.
---
# Sound money = functioning economy
\
Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future.
The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events.
---
# Recessions and debt arise from unsound money
\
Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles.
According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt.
We need to return to sound money and a new gold standard. Enter bitcoin.
---
# Bitcoin is scarce
\
Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued.
The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward.
Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released.
That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value.
---
# Bitcoin is secure
\
The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information.
Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power.
Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value.
---
# Challenges for adoption
\
Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value.
Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended.
Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system.
---

This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading).
‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018.
Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop)
-

@ 7d33ba57:1b82db35
2025-04-02 19:47:25
Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.

## **🏛️ Top Things to See & Do in Trogir**
### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡**
- Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**.
- Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**.
- Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**.
### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪**
- Offers **stunning panoramic views** over Trogir and the Adriatic.
- A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery!
### **3️⃣ Visit Kamerlengo Fortress 🏰**
- A **15th-century Venetian fortress** with **amazing sea views** from the top.
- In summer, it hosts **concerts and cultural events**.
### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊**
- A lively waterfront filled with **cafés, restaurants, and luxury yachts**.
- Perfect for a **relaxing evening walk** while watching the sunset.

### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️**
- **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities.
- **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**.
- **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation.
### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️**
- A **stunning turquoise bay**, perfect for **swimming and snorkeling**.
- Just **a short boat ride from Trogir**.
### **7️⃣ Try Dalmatian Cuisine 🍽️**
- **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟
- **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi.
- **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.

## **🚗 How to Get to Trogir**
✈️ **By Air:**
- **Split Airport (SPU)** is just **10 minutes away**! 🚕
🚘 **By Car:**
- **From Split:** ~30 minutes (27 km)
- **From Zadar:** ~1.5 hours (130 km)
🚌 **By Bus:** Frequent buses run between **Split and Trogir**.
⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.

## **💡 Tips for Visiting Trogir**
✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️
✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅
✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟
✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤
✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷

-

@ cbaa0c82:e9313245
2025-04-02 18:53:57
#TheWholeGrain - #March2025
March of 2025 was a standard month for Bread and Toast. However, it did include a the occasional five Sunday Singles which seems like hitting the jackpot! Talk about lucky!
Included with the five Sunday Singles was two more pages of the Adventure Series: Questline where we saw Bread, Toast, and End-Piece face off against their first adversary!
End-Piece made a first appearance for in Toast's Comic Collection under the title E: The Last Slice while the Concept Art piece was the original drawing of all three slices of bread together. And, last of all we updated the Bitcoin logo because why not!?
**Sunday Singles - March 2025**
2025-03-02 | Sunday Single 82
Title: Slingshot!
*Watch out! Toast is quite the sharpshooter!*
https://i.nostr.build/zHA9C7cOOZLOCl0o.png
2025-03-09 | Sunday Single 83
Title: Puzzles
*End-Piece just figured out the puzzle!*
https://i.nostr.build/u2EBdcsuwO2xo23P.png
2025-03-16 | Sunday Single 84
Title: Basketball
*Oh, the madness!*
https://i.nostr.build/8F1OFFVra7zQOIy6.png
2025-03-23 | Sunday Single 85
Title: Coffee
*The perfect way to start the day.*
https://i.nostr.build/aiGZOvOmow3igru6.png
2025-03-30 | Sunday Single 86
Title: Origami
*End-Piece has a way with paper.*
https://i.nostr.build/0ySzGwF9QnZxwLxD.png
**Adventure Series: Questline**
The group is attacked by a crow with Bread being the target of the giant bird, but with a group of trusty friends any enemy can be defeated!
Artist: Dakota Jernigan (The Bitcoin Painter)
Writer: Daniel David (dan 🍞)
2025-03-11 | Questline
005 - Under Attack
*Toast and End-Piece are able to escape the attack from the giant winged predator, but Bread being distracted by thoughts of the village is caught off guard. End-Piece immediately charges the attacker with a fury of mallet swings. Meanwhile, Toast loads up an arrow with intentions of piercing through the giant bird.*
https://i.nostr.build/F24sd7SFFbsW9WZY.png
2025-03-25 | Questline
006 - A Finished Battle
*End-Piece lands a series of blows to the winged beast. Toast finishes it off with a second arrow to the heart. Bread is only slightly injured, but is more upset about having been so vulnerable due to being so distracted. Moving forward Bread will have to be more vigilant.*
https://i.nostr.build/n5a7Jztq9MHxuGNf.png
**Other Content Released in March 2025**
2025-03-05 | Toast's Comic Collection
Title: E: The Last Slice #11
*A gluten-based pandemic has killed off all slices of bread that are not Toast except for one slice of bread that happens to be an end piece.*
https://i.nostr.build/aar20oHAAKmZOovD.png
2025-03-12 | Concept Art
Title: Original Bread and Toast
*This was the first drawing of all three characters together. It was used a lot for branding when the project first started up in 2023.*
https://i.nostr.build/yqkmBuTiH8AKbCzI.png
2025-03-19 | Bitcoin Art
Title: Bitcoin/Bread
Block Height: 888566
*Two things that just go together.*
https://i.nostr.build/MDPkzOPVEaOJVTFE.png
Thanks for checking out the seventh issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com!
**So long, March!**
***Bread, Toast, and End-Piece***
#BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #🍞 #🖼️
***List of nPubs Mentioned:***
The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g
dan 🍞:
npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6
-

@ 17538dc2:71ed77c4
2025-04-02 16:04:59
The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised.
### macOS Sequoia 15.4
Released March 31, 2025
Accessibility
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance
AccountPolicy
Available for: macOS Sequoia
Impact: A malicious app may be able to gain root privileges
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24234: an anonymous researcher
AirDrop
Available for: macOS Sequoia
Impact: An app may be able to read arbitrary file metadata
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24097: Ron Masas of BREAKPOINT.SH
App Store
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24276: an anonymous researcher
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24272: Mickey Jin (@patch1t)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A downgrade issue was addressed with additional code-signing restrictions.
CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: A malicious app may be able to read or write to protected files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos.
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A privacy issue was addressed by removing the vulnerable code.
CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk)
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted file may lead to arbitrary code execution
Description: The issue was addressed with improved memory handling.
CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Authentication Services
Available for: macOS Sequoia
Impact: Password autofill may fill in passwords after failing authentication
Description: This issue was addressed through improved state management.
CVE-2025-30430: Dominik Rath
Authentication Services
Available for: macOS Sequoia
Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix
Description: The issue was addressed with improved input validation.
CVE-2025-24180: Martin Kreichgauer of Google Chrome
Authentication Services
Available for: macOS Sequoia
Impact: A malicious app may be able to access a user's saved passwords
Description: This issue was addressed by adding a delay between verification code attempts.
CVE-2025-24245: Ian Mckay (@iann0036)
Automator
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed by removing vulnerable code and adding additional checks.
CVE-2025-30460: an anonymous researcher
BiometricKit
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24237: Yutong Xiu
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A path handling issue was addressed with improved validation.
CVE-2025-30429: Denis Tokarev (@illusionofcha0s)
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with improved checks.
CVE-2025-24212: Denis Tokarev (@illusionofcha0s)
CloudKit
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-24215: Kirin (@Pwnrin)
CoreAudio
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: The issue was addressed with improved checks.
CVE-2025-24163: Google Threat Analysis Group
CoreAudio
Available for: macOS Sequoia
Impact: Playing a malicious audio file may lead to an unexpected app termination
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: This issue was addressed with improved memory handling.
CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia Playback
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: A path handling issue was addressed with improved validation.
CVE-2025-30454: pattern-f (@pattern_F_)
CoreServices
Description: This issue was addressed through improved state management.
CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
CoreText
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Crash Reporter
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher
curl
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-9681
Disk Images
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A file access issue was addressed with improved input validation.
CVE-2025-24255: an anonymous researcher
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-30456: Gergely Kalman (@gergely_kalman)
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24267: an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova
dyld
Available for: macOS Sequoia
Impact: Apps that appear to use App Sandbox may be able to launch without restrictions
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com)
FaceTime
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky)
FeedbackLogger
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved data protection.
CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf)
Focus
Available for: macOS Sequoia
Impact: An attacker with physical access to a locked device may be able to view sensitive user information
Description: The issue was addressed with improved checks.
CVE-2025-30439: Andr.Ess
Focus
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24283: Kirin (@Pwnrin)
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards.
CVE-2025-30461: an anonymous researcher
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was resolved by sanitizing logging
CVE-2025-30447: LFY@secsys from Fudan University
Foundation
Available for: macOS Sequoia
Impact: An app may be able to cause a denial-of-service
Description: An uncontrolled format string issue was addressed with improved input validation.
CVE-2025-24199: Manuel Fernandez (Stackhopper Security)
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2025-30464: ABC Research s.r.o.
CVE-2025-24273: Wang Yu of Cyberserval
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to disclose kernel memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike
Handoff
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-30463: mzzzz__
ImageIO
Available for: macOS Sequoia
Impact: Parsing an image may lead to disclosure of user information
Description: A logic error was addressed with improved error handling.
CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative
Installer
Available for: macOS Sequoia
Impact: An app may be able to check the existence of an arbitrary path on the file system
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Installer
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data
Description: A logic issue was addressed with improved checks.
CVE-2025-24229: an anonymous researcher
IOGPUFamily
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or write kernel memory
Description: An out-of-bounds write issue was addressed with improved input validation.
CVE-2025-24257: Wang Yu of Cyberserval
IOMobileFrameBuffer
Available for: macOS Sequoia
Impact: An app may be able to corrupt coprocessor memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security
Kerberos Helper
Available for: macOS Sequoia
Impact: A remote attacker may be able to cause unexpected app termination or heap corruption
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2025-24235: Dave G.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: The issue was addressed with improved checks.
CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24203: Ian Beer of Google Project Zero
Kernel
Available for: macOS Sequoia
Impact: An attacker with user privileges may be able to read kernel memory
Description: A type confusion issue was addressed with improved memory handling.
CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL
LaunchServices
Available for: macOS Sequoia
Impact: A malicious JAR file may bypass Gatekeeper checks
Description: This issue was addressed with improved handling of executable types.
CVE-2025-24148: Kenneth Chew
libarchive
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-48958
Libinfo
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: An integer overflow was addressed with improved input validation.
CVE-2025-24195: Paweł Płatek (Trail of Bits)
libnetcore
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may result in the disclosure of process memory
Description: A logic issue was addressed with improved checks.
CVE-2025-24194: an anonymous researcher
libxml2
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2025-27113
CVE-2024-56171
libxpc
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed through improved state management.
CVE-2025-24178: an anonymous researcher
libxpc
Available for: macOS Sequoia
Impact: An app may be able to delete files for which it does not have permission
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc)
libxpc
Available for: macOS Sequoia
Impact: An app may be able to gain elevated privileges
Description: A logic issue was addressed with improved checks.
CVE-2025-24238: an anonymous researcher
Mail
Available for: macOS Sequoia
Impact: "Block All Remote Content" may not apply for all mail previews
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24172: an anonymous researcher
manpages
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30450: Pwn2car
Maps
Available for: macOS Sequoia
Impact: An app may be able to read sensitive location information
Description: A path handling issue was addressed with improved logic.
CVE-2025-30470: LFY@secsys from Fudan University
NetworkExtension
Available for: macOS Sequoia
Impact: An app may be able to enumerate a user's installed apps
Description: This issue was addressed with additional entitlement checks.
CVE-2025-30426: Jimmy
Notes
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24262: LFY@secsys from Fudan University
NSDocument
Available for: macOS Sequoia
Impact: A malicious app may be able to access arbitrary files
Description: This issue was addressed through improved state management.
CVE-2025-24232: an anonymous researcher
OpenSSH
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An injection issue was addressed with improved validation.
CVE-2025-24246: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24261: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A logic issue was addressed with improved checks.
CVE-2025-24164: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: A malicious app with root privileges may be able to modify the contents of system files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0)
Parental Controls
Available for: macOS Sequoia
Impact: An app may be able to retrieve Safari bookmarks without an entitlement check
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24259: Noah Gregory (wts.dev)
Photos Storage
Available for: macOS Sequoia
Impact: Deleting a conversation in Messages may expose user contact information in system logging
Description: A logging issue was addressed with improved data redaction.
CVE-2025-30424: an anonymous researcher
Power Services
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24173: Mickey Jin (@patch1t)
Python
Available for: macOS Sequoia
Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2023-27043
RPAC
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved validation of environment variables.
CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to user interface spoofing
Description: The issue was addressed with improved UI.
CVE-2025-24113: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to address bar spoofing
Description: The issue was addressed with improved checks.
CVE-2025-30467: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: A website may be able to access sensor information without user consent
Description: The issue was addressed with improved checks.
CVE-2025-31192: Jaydev Ahire
Safari
Available for: macOS Sequoia
Impact: A download's origin may be incorrectly associated
Description: This issue was addressed through improved state management.
CVE-2025-24167: Syarif Muhammad Sajjad
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access removable volumes without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit)
Sandbox
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: The issue was addressed with improved checks.
CVE-2025-30452: an anonymous researcher
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24181: Arsenii Kostromin (0x3c3e)
SceneKit
Available for: macOS Sequoia
Impact: An app may be able to read files outside of its sandbox
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30458: Mickey Jin (@patch1t)
Security
Available for: macOS Sequoia
Impact: A remote user may be able to cause a denial-of-service
Description: A validation issue was addressed with improved logic.
CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington
Security
Available for: macOS Sequoia
Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data
Description: This issue was addressed with improved access restrictions.
CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog)
Share Sheet
Available for: macOS Sequoia
Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started
Description: This issue was addressed with improved access restrictions.
CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: A permissions issue was addressed with improved validation.
CVE-2025-30465: an anonymous researcher
Shortcuts
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24280: Kirin (@Pwnrin)
Shortcuts
Available for: macOS Sequoia
Impact: A Shortcut may run with admin privileges without authentication
Description: An authentication issue was addressed with improved state management.
CVE-2025-31194: Dolf Hoegaerts
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: This issue was addressed with improved access restrictions.
CVE-2025-30433: Andrew James Gonzalez
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk)
Siri
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-24217: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A privacy issue was addressed by not logging contents of text fields.
CVE-2025-24214: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to enumerate devices that have signed into the user's Apple Account
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L
Siri
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An authorization issue was addressed with improved state management.
CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Siri
Available for: macOS Sequoia
Impact: An attacker with physical access may be able to use Siri to access sensitive user data
Description: This issue was addressed by restricting options offered on a locked device.
CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security
SMB
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: The issue was addressed with improved memory handling.
CVE-2025-24269: Alex Radocea of Supernetworks
SMB
Available for: macOS Sequoia
Impact: Mounting a maliciously crafted SMB network share may lead to system termination
Description: A race condition was addressed with improved locking.
CVE-2025-30444: Dave G.
SMB
Available for: macOS Sequoia
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL
smbx
Available for: macOS Sequoia
Impact: An attacker in a privileged position may be able to perform a denial-of-service
Description: The issue was addressed with improved memory handling.
CVE-2025-24260: zbleet of QI-ANXIN TianGong Team
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Software Update
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24254: Arsenii Kostromin (0x3c3e)
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
StickerKit
Available for: macOS Sequoia
Impact: An app may be able to observe unprotected user data
Description: A privacy issue was addressed by moving sensitive data to a protected location.
CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania
Storage Management
Available for: macOS Sequoia
Impact: An app may be able to enable iCloud storage features without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A race condition was addressed with additional validation.
CVE-2025-24240: Mickey Jin (@patch1t)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to bypass Privacy preferences
Description: A race condition was addressed with additional validation.
CVE-2025-31188: Mickey Jin (@patch1t)
Summarization Services
Available for: macOS Sequoia
Impact: An app may be able to access information about a user's contacts
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk)
System Settings
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24278: Zhongquan Li (@Guluisacat)
System Settings
Available for: macOS Sequoia
Impact: An app with root privileges may be able to access private information
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
SystemMigration
Available for: macOS Sequoia
Impact: A malicious app may be able to create symlinks to protected regions of the disk
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30457: Mickey Jin (@patch1t)
Voice Control
Available for: macOS Sequoia
Impact: An app may be able to access contacts
Description: This issue was addressed with improved file handling.
CVE-2025-24279: Mickey Jin (@patch1t)
Web Extensions
Available for: macOS Sequoia
Impact: An app may gain unauthorized access to Local Network
Description: This issue was addressed with improved permissions checking.
CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven
Web Extensions
Available for: macOS Sequoia
Impact: Visiting a website may leak sensitive data
Description: A script imports issue was addressed with improved isolation.
CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: The issue was addressed with improved memory handling.
WebKit Bugzilla: 285892
CVE-2025-24264: Gary Kwong, and an anonymous researcher
WebKit Bugzilla: 284055
CVE-2025-24216: Paul Bakker of ParagonERP
WebKit
Available for: macOS Sequoia
Impact: A type confusion issue could lead to memory corruption
Description: This issue was addressed with improved handling of floats.
WebKit Bugzilla: 286694
CVE-2025-24213: Google V8 Security Team
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected process crash
Description: A buffer overflow issue was addressed with improved memory handling.
WebKit Bugzilla: 286462
CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: A use-after-free issue was addressed with improved memory management.
WebKit Bugzilla: 285643
CVE-2025-30427: rheza (@ginggilBesel)
WebKit
Available for: macOS Sequoia
Impact: A malicious website may be able to track users in Safari private browsing mode
Description: This issue was addressed through improved state management.
WebKit Bugzilla: 286580
CVE-2025-30425: an anonymous researcher
WindowServer
Available for: macOS Sequoia
Impact: An attacker may be able to cause unexpected app termination
Description: A type confusion issue was addressed with improved checks.
CVE-2025-24247: PixiePoint Security
WindowServer
Available for: macOS Sequoia
Impact: An app may be able to trick a user into copying sensitive data to the pasteboard
Description: A configuration issue was addressed with additional restrictions.
CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH)
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24266: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2025-24265: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24157: an anonymous researcher
-

@ 8d34bd24:414be32b
2025-04-02 14:13:03
I was reading this passage last night:
> …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine}
Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself.
This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation.
> And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28)
When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect:
> And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine}
When one particular man said that he would follow Jesus anywhere, Jesus responded this way.
> As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine}
Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort.
> “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine}
Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect.
> “**For my thoughts are not your thoughts,\
> neither are your ways my ways**,”\
> declares the Lord.
>
> “As the heavens are higher than the earth,\
> so are **my ways higher than your ways**\
> and my thoughts than your thoughts.
>
> As the rain and the snow\
> come down from heaven,\
> and do not return to it\
> without watering the earth\
> and making it bud and flourish,\
> so that it yields seed for the sower and bread for the eater,\
> so is **my word that goes out from my mouth:\
> It will not return to me empty,\
> but will accomplish what I desire\
> and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine}
God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us.
> Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine}
In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word.
> They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine}
Peter specifically warns believers to expect trials and hardship.
> Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And,
>
> “If it is hard for the righteous to be saved,\
> what will become of the ungodly and the sinner?”
>
> So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine}
Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship.
> …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine}
No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good.
> Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written,
>
> “For Your sake we are being put to death all day long;\
> We were considered as sheep to be slaughtered.”
> ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine}
I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be.
First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard.
Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion.
In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before.
When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good.
We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness.
> Oh, the depth of the riches of the wisdom and knowledge of God!\
> How unsearchable his judgments,\
> and his paths beyond tracing out!\
> “Who has known the mind of the Lord?\
> Or who has been his counselor?”\
> “Who has ever given to God,\
> that God should repay them?”\
> For from him and through him and for him are all things.\
> To him be the glory forever! Amen. (Romans 11:33-36)
Trust Jesus
-

@ f3873798:24b3f2f3
2025-04-02 13:50:17
O Bitcoin e as criptomoedas surgiram como uma alternativa descentralizada ao sistema financeiro tradicional. No entanto, no Brasil, o **Sistema Financeiro Nacional (SFN)** tem adotado medidas para controlar e limitar a exposição de investidores e instituições a esses ativos. Neste artigo, exploraremos as principais resoluções e regulamentações que restringem o investimento em Bitcoin no país.
## **O Posicionamento do Banco Central do Brasil (Bacen)**

O Banco Central do Brasil (Bacen) e outros órgãos reguladores, como a **Comissão de Valores Mobiliários (CVM)**, têm adotado uma postura cautelosa em relação às criptomoedas.
### **Resolução Bacen nº 4.753/2021**
- Proíbe que instituições financeiras ofereçam serviços de criptomoedas em suas carteiras sem autorização prévia.
- Restringe bancos e corretoras de operarem diretamente com criptoativos, limitando sua integração ao sistema financeiro tradicional.
### **Comunicado do Bacen sobre Riscos das Criptomoedas**
- O Bacen já emitiu alertas sobre os riscos de volatilidade, fraudes e falta de garantias em investimentos em Bitcoin.
- Recomenda que investidores tratem criptomoedas como ativos de alto risco.
---
## A CVM e as Restrições a Fundos de Investimento em Bitcoin
A **CVM** tem sido mais restritiva que o Bacen em relação a produtos financeiros baseados em criptomoedas.
### **Deliberação CVM nº 175/2022**
- Proíbe fundos de investimento no exterior (FIE) de alocarem mais de **10% do patrimônio** em criptomoedas.
- Impede que fundos multimercados brasileiros tenham exposição direta a Bitcoin e outras criptomoedas.
### **Instrução CVM nº 555/2021**
- Estabelece que **ETFs de Bitcoin** não podem ser comercializados no Brasil sem aprovação expressa da CVM.
- Até hoje, nenhum ETF de criptomoeda foi aprovado no país.
---
## **Tributação e Controles da Receita Federal**
Além das restrições do Bacen e da CVM, a **Receita Federal** impõe regras rígidas para transações em Bitcoin:
### **Instrução Normativa RFB nº 1.888/2019**
- Obriga declaração de todas as operações em criptomoedas acima de **R$ 35 mil** por mês.
- Tributa ganhos de capital em criptomoedas em **15% a 22,5%**, dependendo do valor.
---
## **O Bitcoin Sob Vigilância do SFN**
O Sistema Financeiro Nacional tem adotado medidas para **limitar a adoção em massa do Bitcoin**, seja por meio de regulamentações rígidas, restrições a fundos ou alertas sobre riscos.
Enquanto o mercado de criptomoedas cresce globalmente, no Brasil ainda há um **cenário de cautela e controle**, com o SFN buscando evitar que criptomoedas desafiem a hegemonia do sistema financeiro tradicional.
-

@ 06639a38:655f8f71
2025-04-02 13:47:57
You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github.
Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits.
Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19)
### **TLV's**
Things were getting more complicated with the other prefixes / identifiers defined in NIP-19:
* `nevent`
* `naddr`
* `nprofile`
This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's.
_When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._
_For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._
These possible standardized `TLV` types are:
* `0`_:_ `special`
* _depends on the bech32 prefix:_
* _for_ `nprofile` _it will be the 32 bytes of the profile public key_
* _for_ `nevent` _it will be the 32 bytes of the event id_
* _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._
* `1`_:_ `relay`
* _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_
* _this may be included multiple times_
* `2`_:_ `author`
* _for_ `naddr`_, the 32 bytes of the pubkey of the event_
* _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_
* `3`_:_ `kind`
* _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_
* _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_
These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters.
Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code):
* [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74)
* [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19)
### **So what's next?**
* NIP-19 code housekeeping + refactoring
* Prepare a new release with NIP-19 integration
* Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev)
-

@ 5d4b6c8d:8a1c1ee3
2025-04-02 13:15:30
I've always loved Westbrook. He plays so hard and does things through sheer force of will that no one else has ever been able to do. He's also the last guy you want on the court at the end of close games.
No one has ever so reliably made poor choices in late game, or even just end of clock, situations. Here are some highlights from the epic Nuggets vs T-Wolves game, which Russ completely blew at the end.
https://youtu.be/rgtzQxRpH6c
I've said before that I think Russ' career +/- would be 4 points higher if coaches had never let him play at the ends of quarters. Translation for non-analytics nerds: Russ has blown virtually every final possession throughout his entire career. It's unbelievable.
Is there anyone I'm overlooking as a worse clutch performer?
originally posted at https://stacker.news/items/932077
-

@ fd06f542:8d6d54cd
2025-04-02 12:45:44
## 国内开发者作品展
### jumble.social
作品: https://jumble.social/
其他作品 :
Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
Building 👨💻:
https://github.com/CodyTseng/jumble
https://github.com/CodyTseng/nostr-relay-tray
https://github.com/CodyTseng/danmakustr
https://github.com/CodyTseng/nostr-relay-nestjs
https://github.com/CodyTseng/nostr-relay
https://github.com/CodyTseng
### nostrbook.com
作品: https://nostrbook.com
- NostrBridge, 网桥转发
- TaskQ5, 分布式多任务
- NostrHTTP, nostr to http
- Postr, 匿名交友,匿名邮局
- nostrclient (Python client) .
-nostrbook, (nostrbook.com) 用nostr在线写书
https://www.duozhutuan.com nostrhttp demo
https://github.com/duozhutuan/NostrBridge
### nostrmo
A nostr dev.
#Nostrmo A client support all platform.
#Nowser A nostr signing project.
#CacheRelay A nostr cache relay peject.
#cfrelay A nostr relay base on cloudflare wokers.
A nostr note timing send service. https://sendbox.nostrmo.com/
https://github.com/haorendashu/nostrmo
### nostrudel
avaScript developer working on some nostr stuff
- noStrudel https://nostrudel.ninja/
- Blossom https://github.com/hzrd149/blossom
- Applesauce https://hzrd149.github.io/applesauce/
https://hzrd149.com/
### nostrudel
A nostr web client focused on exploring the nostr protocol
https://geyser.fund/project/nostrudel
-

@ 7bdef7be:784a5805
2025-04-02 12:37:35
The following script try, using [nak](https://github.com/fiatjaf/nak), to find out the last ten people who have followed a `target_pubkey`, sorted by the most recent. It's possibile to shorten `search_timerange` to speed up the search.
```
#!/usr/bin/env fish
# Target pubkey we're looking for in the tags
set target_pubkey "6e468422dfb74a5738702a8823b9b28168abab8655faacb6853cd0ee15deee93"
set current_time (date +%s)
set search_timerange (math $current_time - 600) # 24 hours = 86400 seconds
set pubkeys (nak req --kind 3 -s $search_timerange wss://relay.damus.io/ wss://nos.lol/ 2>/dev/null | \
jq -r --arg target "$target_pubkey" '
select(. != null and type == "object" and has("tags")) |
select(.tags[] | select(.[0] == "p" and .[1] == $target)) |
.pubkey
' | sort -u)
if test -z "$pubkeys"
exit 1
end
set all_events ""
set extended_search_timerange (math $current_time - 31536000) # One year
for pubkey in $pubkeys
echo "Checking $pubkey"
set events (nak req --author $pubkey -l 5 -k 3 -s $extended_search_timerange wss://relay.damus.io wss://nos.lol 2>/dev/null | \
jq -c --arg target "$target_pubkey" '
select(. != null and type == "object" and has("tags")) |
select(.tags[][] == $target)
' 2>/dev/null)
set count (echo "$events" | jq -s 'length')
if test "$count" -eq 1
set all_events $all_events $events
end
end
if test -n "$all_events"
echo -e "Last people following $target_pubkey:"
echo -e ""
set sorted_events (printf "%s\n" $all_events | jq -r -s '
unique_by(.id) |
sort_by(-.created_at) |
.[] | @json
')
for event in $sorted_events
set npub (echo $event | jq -r '.pubkey' | nak encode npub)
set created_at (echo $event | jq -r '.created_at')
if test (uname) = "Darwin"
set follow_date (date -r "$created_at" "+%Y-%m-%d %H:%M")
else
set follow_date (date -d @"$created_at" "+%Y-%m-%d %H:%M")
end
echo "$follow_date - $npub"
end
end
```
-

@ fd06f542:8d6d54cd
2025-04-02 12:34:07
- [首页](/readme.md)
- [国内开发者](/01.md)
-

@ 7bdef7be:784a5805
2025-04-02 12:12:12
We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs.
## The problem
Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so **everyone can actually snoop what we are interested in**, and what is supposable that we read daily.
## The solution
Nostr has a simple solution for this necessity: **encrypted lists**.
Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, **we can hide the lists' content from others**.
The implications are obvious: we can not only have a more organized way to browse content, but it is also **really private one**.
One might wonder what use can really be made of private lists; here are some examples:
* Browse “can't miss” content from users I consider a priority;
* Supervise competitors or adversarial parts;
* Monitor sensible topics (tags);
* Following someone without being publicly associated with them, as this may be undesirable;
The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of **how many bots scan our actions to profile us**.
## The current state
Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity.
Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an **easier option** to start offering private lists: give the user **the possibility to simply mark them as local-only**, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment.
To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage **both encrypted and local-only lists**.
Beg your Nostr client to implement private lists!
-

@ 7bdef7be:784a5805
2025-04-02 12:02:45
We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, \*\*so everyone can actually snoop\*\* what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see \[NIP-51\](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create \*\*dedicated feeds\*\*, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be \*\*encrypted\*\*, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also \*\*really private one\*\*. One might wonder what use can really be made of private lists; here are some examples: - Browse “can't miss” content from users I consider a priority; - Supervise competitors or adversarial parts; - Monitor sensible topics (tags); - Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of \*\*how many bots scan our actions to profile us\*\*. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff (\[NIP-44\](https://github.com/nostr-protocol/nips/blob/master/51.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply \*\*mark them as local-only\*\*, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is Gossip, which permits to manage \*\*both encrypted and local-only lists\*\*. Beg your Nostr client to implement private lists!
-

@ 8dac122d:0fc98d37
2025-04-02 10:46:20

When selling goods or services, you might want to consider using an auction format to maximize your profits and customer satisfaction. For those of us that don't know, selling through auction is the way where the price of the item is determined by the bids of the buyers, rather than by the seller. It's an interesting approach when trying to attract more buyers and generate more exposure. It can generate a buzz around your item and business, drawing attention from potential buyers who might not otherwise be interested, with any healthier word-of-mouth marketing and social media sharing.
Lately I've been reserching on this topic, thinking on how it could be implemented here on SN. Exploring other forums with more and fewer functionalities, have noticed that some really dive in with years of experience, trust build systems and the ability to offer this service with honesty and confidence. It's curious to see how all this started back in Babylon around 500 B.C., with brides as earliest known auctions “items” sold to grooms through descending bids. I'll leave you to research and discover _why_. Hopefully, ~AGORA auctions will be less problematic!
# How do we reach Online Auctions perfection
Firstly, I want to give you some history about “remote” auctions and how they have been evolving together with technological innovations. When TV and telephones were widely adopted in the west early in the late 80s, Nigel Myers, Director for Cox Automotive, describes the shifting mindset towards technology as: _“a time when people were really beginning to grasp what technology could do and that traditional ways of working were going to be challenged. We adopted the view that we must embrace these emerging technologies before our competitors. We considered it essential to remain at the forefront of the industry._”

AuctionVision in 1991 was the industry’s first successful intent into _“virtual auctions”_, it offered the ability to buy and sell vehicles remotely for the very first time via satellite television. It revolutionized the industry that had remained largely the same for decades and provided the foundations for what we know as online auctions today. Anyone familiar with the telethon events that were popular in the 80s and 90s can picture the scene[^1].
These auctions eventually moved and take more and more place through text-based groups and discussion lists. Yes, those times when cool UIs were not a thing, and one had to connect through the telephone line. Despite the technological challenges, such trades witnessed a huge popularity in those days and seeing the flourishing success of online trading, entrepreneurs began to realize the tremendous potential of online auctions. They understood the global reach online auction markets could have.
<sub>Ebay's AuctionWeb.com website launch in 1996</sub>

It was in 1995 that the first simple online auction website was made available by Pierre Omidyar, In September 1997, the portal was officially renamed from AuctionWeb.com to eBay.com.[^2] Being the first such venture in the market, eBay had many advantages, which they utilized fully quickly becaming the biggest player in this industry. They have maintained their reputation till today, however, various websites soon came up and emerged as strong competitors to eBay. The leading competitors were Yahoo! Auctions and Amazon.com. Today we see an explosion of auction' website that cover specific markets, from cars to RE, art, clothes, snickers, Pokémon's cards , NFTs and who know how many more.
# The various Auctions Formats
Together with technological evolution, auctions have been adapting and evolving to market request satisfying specific needs. Let's break down the various types of auctions formats to evaluate which one could be better suited for the AGORA marketplace.
#### English Auction
Running with ascending bids, this is the most known and adopted worldwide. An initial value is usually defined by the auctioneer as a starting bid, meaning no less than that amount will be accepted. Bidders openly compete by raising the price with bids until the highest bid wins.
It's one of the oldest formats, dating back to ancient Rome (literally called _auctus_), where soldiers auctioned war loot. Modern English auctions quickly evolved in 17th-century England for antiques and art: the Mona Lisa was almost sold in 1959 but was withdrawn when bidding stalled at $5 million (a fraction of its value today).
I see this as a perfect match for our case, as it's the easiest to run manually, bids could be simply public comments for the auctioneer to easily track progress and evaluate the winner. It could be left open until no one else set more bids, or ending on a defied time set as deadline.
#### Dutch Auction
It is not a case, it runs with descending bids. Named as Dutch auction because it was firstly adopted in 17th-cetury's Holland to sell big quantities of perishable items like tulip bulbs (yes, that tulip mania), that if not sold quickly would end up being unsellable. The auctioneer, in this case, sets an intentionally high initial price, bids value were publicly dropped until a buyer screamed _“Mij!”_ (_Mine!_ in English) to confirm interest and stop the auctioneer lowering the price more to have more bidders interested.
Today, tech helps with that: digital clocks sync with global logistics. Flowers bought by 10 AM are shipped by noon and sold in NYC by the next day. The Aalsmeer complex is 1.6 million m² (≈200 soccer fields)[^3]. Forklifts zip through 100+ km of corridors, selling over 12 billion flowers a year. Nearly 80% of global flowers, with some lots dropping from €10 to €0.50 in minutes when bidders sense oversupply. They are also called _Clock Auction_, as the price drops by the second. Bidders just need to simply press a button and get the item.
<sub>Auction board from the Aalsmeer in Holland</sub>

This would be a bit harder to run here, as it would be the auctioneer making lower and lower offers in the in comments. Bidders stay unnotably silent until interested. But the Auctioner couls also be the only spectator... Fun Fact: Google’s 2004 IPO tried a Dutch auction to “democratize” share pricing, it was probably more a sealed-bid auction, but anyway, some say it wasn't a success.
#### Sealed-Bid Auction
First higher price win: due to this nature, it's probably obvious, it was popularized by governments, specifically for procurement contracts. For example, the U.S. Treasury Inc. has used it since the 1800s to sell bonds to bidders that privately submit offers.
The auctioneer reserve the right to close receiving offers at a certain time, or when enough offers have been received to be able to select the highest(s) or the most interesting one(s). As you can understand, bidders often suffer the _winner’s curse_, most of the time ending up overpaying due to the secrecy detail.
We cannot sto auctionees from posting these, but from a bidder or buyer perspective, I'd advise avoiding the participation on this format on SN. It is much riskier for the bidder and definitely doesn't much our value of transparency. Just mentioning as it is part of my research.
#### Vickrey Auction (Second-Price Sealed Bid)
Similar to the Sealed-bid auction, with the only difference that the winner pays the second-highest bid, for example, if you bid 0.05 BTC, and next highest is 0.04 BTC, you win the auction, but you pay 0.04 BTC. This approach, born as improvement of the previous one, incentivize to bid the true max value without penalty for honesty.
Named after William Vickrey, a Nobel-winning economist who designed it in 1961 to incentivize a more truthful bidding format. A practical example are the Government (again) Spectrum Sales, where FCC uses Vickrey-inspired formats to allocate radio frequencies more fairly and try to avoid bid inflation. Good fit for stackers? Definitely not!
#### Other Formats & Variations
Along the centuries, auctions have evolved. Those mentioned above are the most common and adopted. Other really specific formats have been designed to fit specific markets or occasions. For example, **Silent Auctions** are an English Auction's variation, with the only difference that bids are anonymously offered in writing. Mostly used for fundraising and Ads placements, where the bidders prefer to keep certain levels of privacy.
**Penny (or Incremental) Auction** is one where participants pay (historically was just 1 penny to join in, from here the name of the format) to place bids. The timer resets with each bid. Highly risky when applied to online auctions because bidders need to pay for participating. I'll avoid mentioning controversies and scams in history related to this format. Just note down that, to participate, you must really know and have full trust in the auctioneer or the people selling the items.
**Reserve Auction** is where the seller or auctioneer sets a hidden minimum price; if unmet, the item will remain unsold. This could fit here: an auctioneer maybe just need to clearly state “Reserve Met” or “Reserve NOT met” publicly to close the auction, without the need to publicly disclose it in the initial post.
Here a simpler table comparison with evaluation criteria for possible SN'~AGORA implementation
| <sub>Format</sub> | <sub>Transparency</sub> | <sub>Trust Needed</sub> | <sub>Complexity</sub> | <sub>Fraud Risk</sub> | <sub>SN Feasibility</sub> | <sub>Best For</sub> |
|------------------------|------------------|-------------------|----------------|----------------|--------------------|---------------------------------|
| <sub>English</sub> | <sub>High</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>Moderate</sub> | <sub>✅ High</sub> | <sub>Common goods</sub> |
| <sub>No-Reserve</sub> | <sub>High</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>High*</sub> | <sub>✅ High</sub> | <sub>Quick sales, liquidations</sub> |
| <sub>Reserve</sub> | <sub>High</sub> | <sub>Medium†</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>✅ High</sub> | <sub>High-value/rare items</sub> |
| <sub>Dutch</sub> | <sub>Medium</sub> | <sub>High‡</sub> | <sub>High</sub> | <sub>Moderate</sub> | <sub>⚠️ Medium</sub> | <sub>Bulk items, time-sensitive sales</sub> |
| <sub>Silent</sub> | <sub>Medium</sub> | <sub>Medium</sub> | <sub>Low</sub> | <sub>Moderate</sub> | <sub>✅ High</sub> | <sub>Charity, small-scale auctions</sub> |
| <sub>Sealed-Bid</sub> | <sub>Low</sub> | <sub>Very High</sub> | <sub>Medium</sub> | <sub>High</sub> | <sub>❌ Low</sub> | <sub>Private sales (niche use)</sub> |
| <sub>Vickrey</sub> | <sub>Low</sub> | <sub>Very High</sub> | <sub>High</sub> | <sub>High</sub> | <sub>❌ Low</sub> | <sub>Theory-driven experiments</sub> |
| <sub>Penny</sub> | <sub>High</sub> | <sub>Very High</sub> | <sub>Very High</sub> | <sub>Very High</sub> | <sub>❌ Low</sub> | <sub>(Avoid – predatory by design)</sub> |
```
Notes:
- *No-Reserve: High fraud risk if starting bid is too low.
- †Reserve: Transparency is higher if the reserve is disclosed upfront.
- ‡Dutch: Requires strict timekeeping.
```
#### Would the AGORA succeed?
The challenge to run and monitor auctions on SN still unsolved, at least for me. Considering there's not yet a publicly available rating to identify users' trust within the community, nor a private messaging or escrow service, I'll try my best to find the right matches and offer few options to inspire stackers.
With further research, and I'll put together a draft guide to see what you all think about it. Ideally, receive feedback and together make this happening, fostering a more free and open market incentivizing a wider bitcoin circular economy.
Thanks for reading until here, hope you find it entertaining. I'll leave you with an ending fun fact: In the 1800s, cattle auctions in Dodge City in Kansas used English-style bids, with cowboys literally _shouting_ offers. Deals were sealed with a handshake and whiskey!
[^1]: Manheim at 100: How virtual auctions revolutionized the industry in the 90s
Written by Manheim Content Team - 19/07/2021 - https://www.manheim.co.uk/news/2021/manheim-100-how-virtual-auctions-revolutionised-the-industry-in-the-90s
[^2]: From the Web Design Museum, AuctionWeb in 1996 https://www.webdesignmuseum.org/gallery/ebay-1996
[^3]: Royal FloraHolland Flower Auction https://www.visitaalsmeer.nl/en/location/royal-floraholland-flower-auction/
originally posted at https://stacker.news/items/931997
-

@ d04ecf33:1d62aa90
2025-04-02 09:48:16
## Physical prototyping
3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes.
Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations.
## Prototypers of Ideas
Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop.
However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car.
From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase.
And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc.
So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better.
## Economic Impact
3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare.
Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away.
## Progress
LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators.
If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today.
If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences.
Keep printing ideas and execute on them!
Learn and repeat. The path to success.
#llm #ai #agi #3dp #programming
-

@ a60e79e0:1e0e6813
2025-04-02 08:26:48
*This is a long form note of a post that lives on my Nostr educational website [Hello Nostr](https://hellonostr.xyz).*
So you've got yourself [started](https://hellonostr.xyz/start), you're up to speed with the latest Nostr [jargon](https://hellonostr.xyz/glossary) and you've learned the basics about the [protocol](https://hellonostr.xyz/101), but you're left wanting more!? Well, look no further! This post contains a useful list of Nostr based utilities than can enhance your experience in and around the Nostr protocol.
## Search and Discovery
Getting started with Nostr can sometimes feel like a lonely journey, particularly if you're the first of your friends and family to discover how awesome it can be! These tools can help you discover new content, connect with existing follows from other networks and just generally have a poke around at the different types of content Nostr has to offer.
> Have a hobby or existing community elsewhere? Have a search for it here to find others with shared interests
- **[Nostr.Band](https://nostr.band/)** - Search for people, posts, media and stats literally anything Nostr has to offer!
- **[Nostr.Directory](https://nostr.directory/)** - Find your Twitter follows on Nostr
- **[Awesome Nostr](https://github.com/aljazceru/awesome-nostr#implementations)** - Extensive list of Relay software
- **[Nostr View](https://nostrview.com/)** - Generic Nostr search
<br/>
## Relays
Relays might not be the sexiest of topics, particularly for newcomers to the network, but they are a crucial part of what makes Nostr great. As you become more competent, you'll want to customize your relay selection and maybe even run your own! Here are some great starting points.
> Running a personal relay is a powerful way to improve the redundancy of your Nostr events.
- **[Nostr.Watch](https://next.nostr.watch/)** - Browse, test and research Nostr relays
- **[Nostrwat.ch](https://nostrwat.ch/)** - List of active Nostr relays
- **[Advanced Nostr Search](https://advancednostrsearch.vercel.app/)** - Targetted search with date ranges
- **[Nostr.Wine](https://nostr.wine/)** - Reliable paid Relay
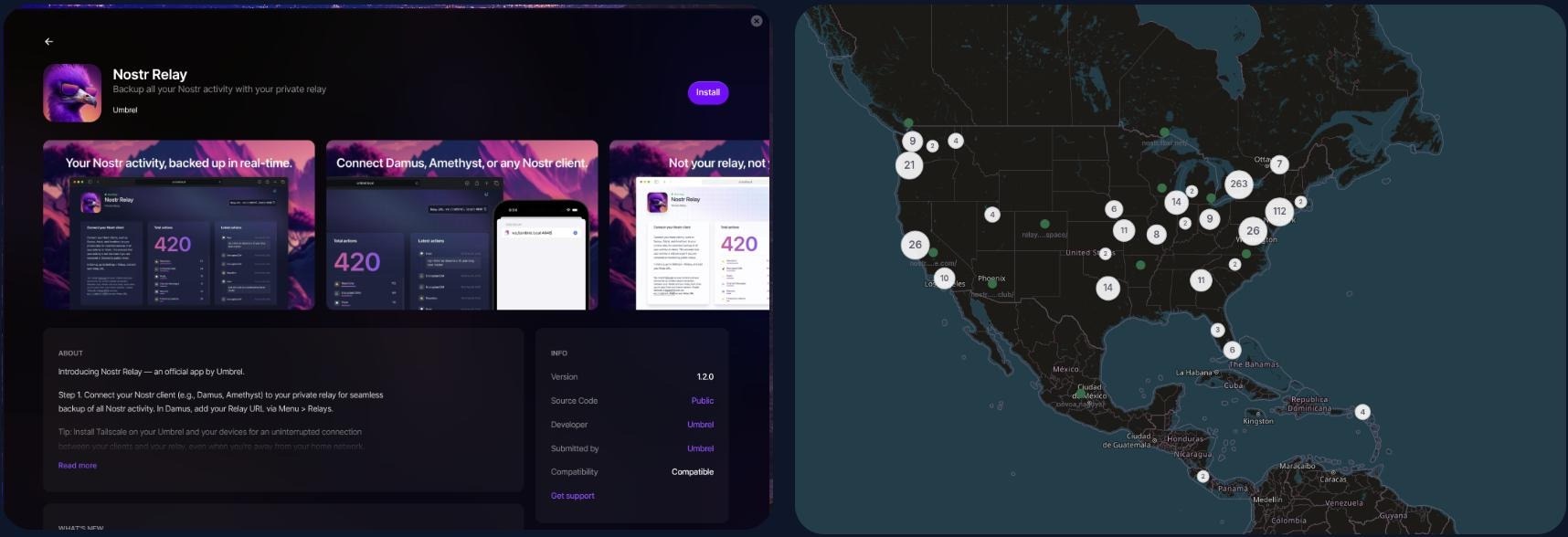
<br/>
## NIP-05 Identity Services
Your nPub, or public key (that long string of letters and numbers) is your ‘official’ Nostr ID, but it’s not exactly catchy. NIP-05 identifiers are a human-readable and easily shareable way to have people find you on Nostr. They look like an email address, like qna@hellonostr.xyz. If you have your own domain
and web server, you can easily [create your own](https://thebitcoinmanual.com/articles/nostr-account-nip-05-verified/) NIP-05 identifier in just a few minutes. If you don't, you'll want to leverage one of the many free or paid solutions.
> Make yourself easier to find on Nostr with a NIP-05 identifier
- **[Bitcoiner.Chat](https://bitcoiner.chat/)** - Free service operated by [QnA](nostr:npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx)
- **[Nostr Plebs](https://nostrplebs.com/)** - Paid service with extra features
- **[Alby](https://getalby.com/)** - Lightning wallet with + NIP-05 solution
- **[Nostr Address](https://en.nostraddress.com/)** - Paid service with extra features
- **[Zaps.Lol](https://zaps.lol/)** - Free service
<br/>
## Key Management
Your private key (or nsec) it the key to your Nostr world. It is what allows you to access and interact with your social graph from any client. It doesn't matter if that client is a micro-blogging app like Amethyst, a podcast app like Fountain, or a P2P marketplace like Plebeian Market, your nsec is paramount to
those interactions. Should your nsec be lost, or fall into the wrong hands, whoever then holds a copy can access Nostr and pretend to be you, meaning that you'll need to start again with a new keypair. Not a nice situation to find yourself in, so treat your nsec VERY carefully.
> Your private key IS your Nostr identity. Treat it with extreme care and do not share it.
- **[Alby](https://getalby.com/)** - Browser extension enabling you to sign into web app without sharing the private key
- **[Nos2x](https://github.com/fiatjaf/nos2x)** - Another browser extension key manager
- **[Keys.Band](https://keys.band/)** - Another browser extension key manager
- **[Amber](https://github.com/greenart7c3/amber)** - Android app for safe nsec storage. Can talk to other clients on the same phone to log in and sign events
- **[Nostr Signing Device](https://github.com/lnbits/nostr-signing-device)** - Dedicated device to store your nsec
- **[Passport](https://docs.foundation.xyz)** - Hardware wallet for offline and deterministic nsec generation and storage
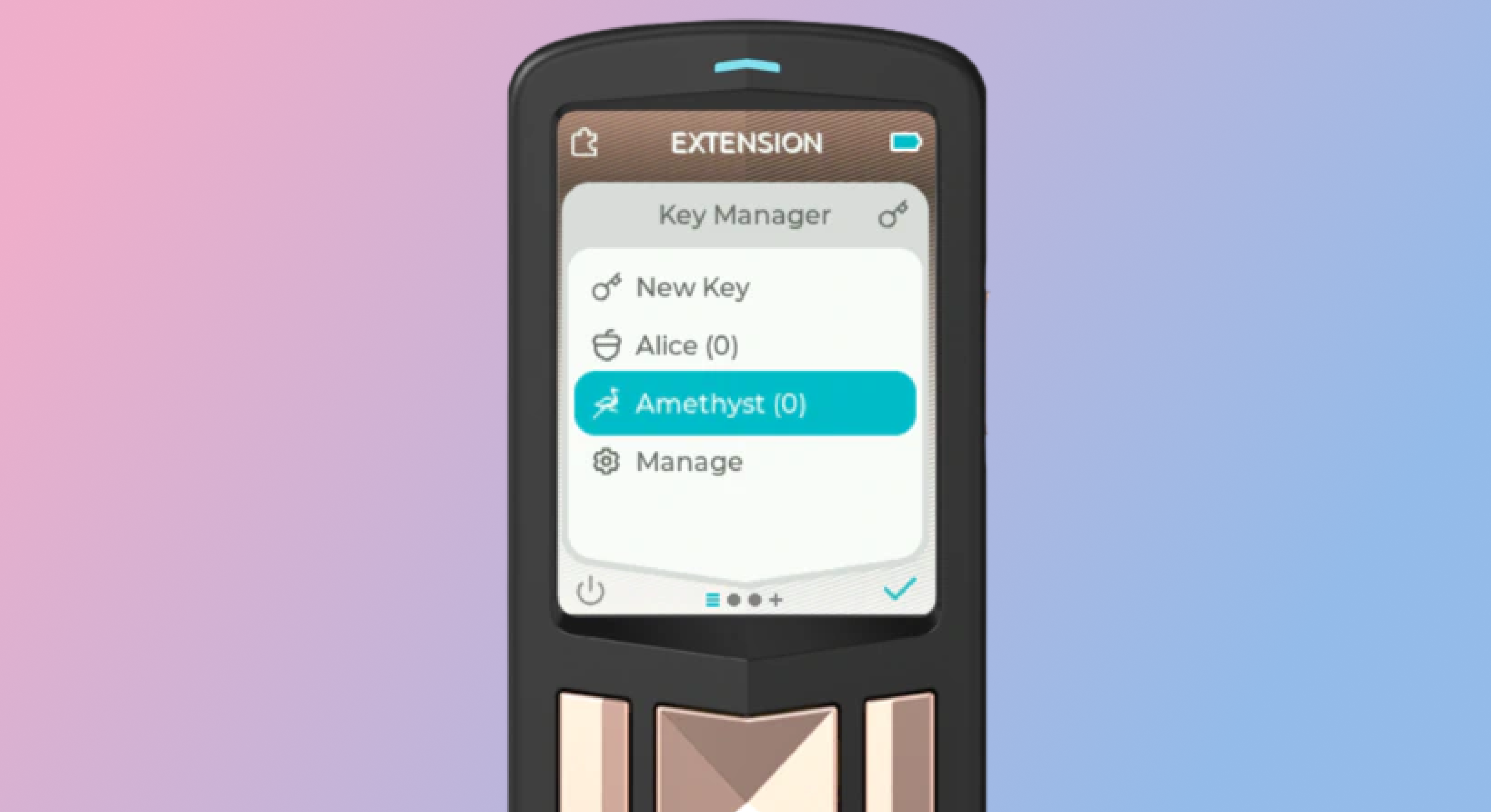
<br/>
## Zap Tools
Zaps are one of the most fun parts of Nostr. Never before have we been able to send fractions of a penny, instantly to our friends because their meme made us laugh, or their blog post was very insightful. Zaps use Bitcoin’s Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider.
- **[Alby](https://getalby.com/)** - Browser extension and self-custodial Lightning wallet
- **[LNBits](https://github.com/lnbits/lnbits)** - A Zap server running on your own Bitcoin node
- **[BTCPay Server](https://btcpayserver.org/)** - Another Zap server running on your own Bitcoin node
- **[Zeus](https://github.com/ZeusLN/zeus)** - Zap compatible self-custodial mobile Lightning wallet
- **[Nostr Wallet Connect](https://nwc.dev/)** - Communication protocol between Lightning wallets and Nostr apps
- **[Ecash Wallets](https://github.com/cashubtc/awesome-cashu)** - Custodial Ecash based wallets that are interoperable with Lightning and Nostr (Funds may be at risk)
- **[Wallet of Satoshi](https://www.walletofsatoshi.com/)** - Custodial Lightning wallet (Funds may be at risk)
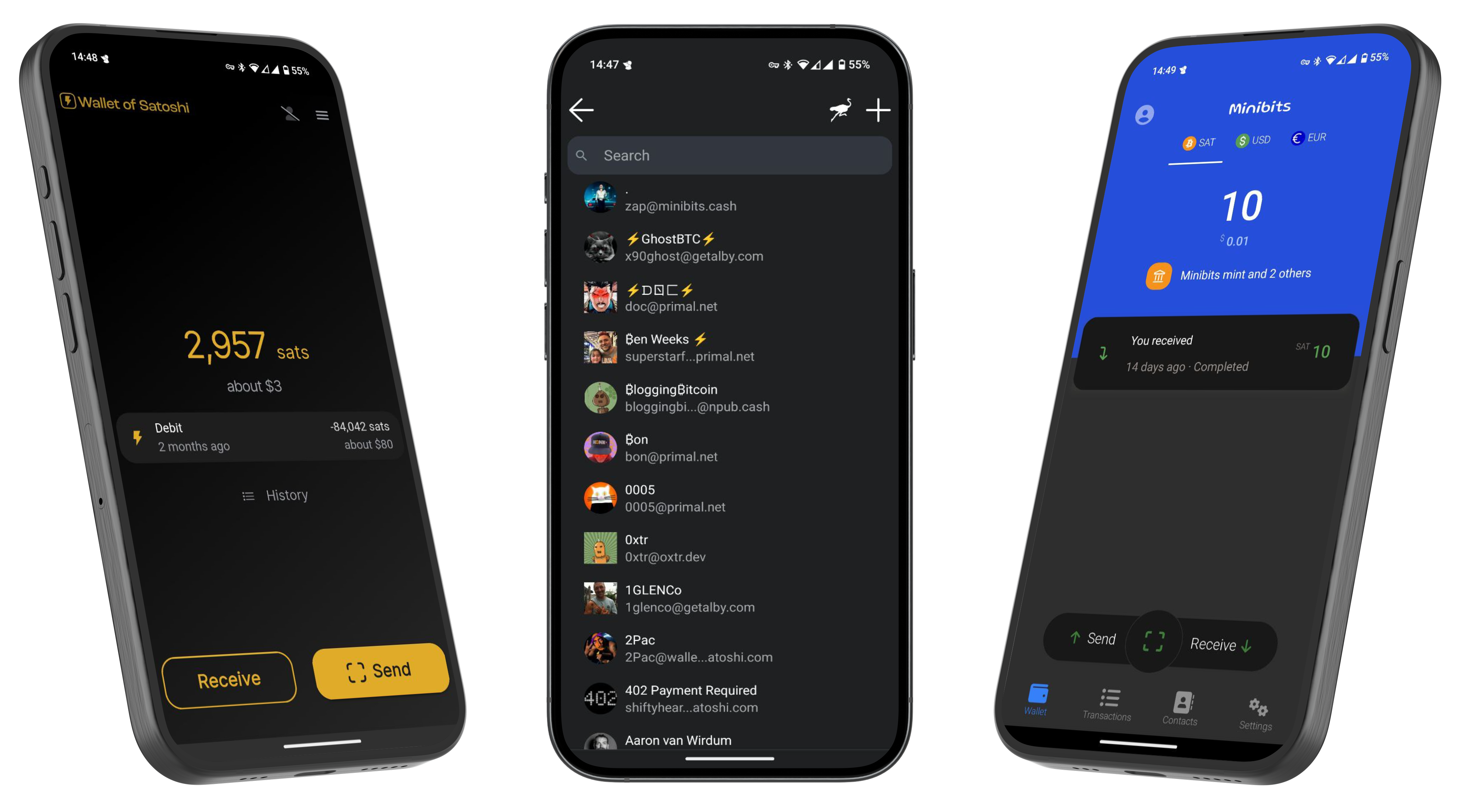
---
If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know
that you found me via this post, I'll be sure to Zap you back! ⚡️
 @ da0b9bc3:4e30a4a9
2025-04-03 07:02:17Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/933122
@ da0b9bc3:4e30a4a9
2025-04-03 07:02:17Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/933122 @ 0f9da413:01bd07d7
2025-04-03 05:32:55 หลังจากจบทริปเที่ยวพัทยาเรียบร้อยแล้วก็ได้เดินทางไปยังเกาะช้างโดยติดรถเจ้าหน้าที่ในที่ทำงานไปไปเกาะช้างครั้งแรกรู้สึกว่ามันไกลเหลือเกินไปค่อนข้างยากหากไม่มีรถส่วนตัว ถ้าให้ไปส่วนตัวก็คงต้องอยู่นานๆ หน่อยชักแบบอาทิตย์หนึ่ง ใช้ชีวิตแบบฝรั่งเที่ยวอยู่ง่ายๆ กินง่ายๆ จากที่ดูในแผนที่ btcmap แล้วพบว่าก็มีร้านที่ปักหมุดไว้อยู่ทั้งหมดสองร้านด้วยกันซึ่งระยะทางก็ค่อนข้างซันเหมือนกัน และมีเนินสูงต่ำสลับกันไป หากไม่มีรถส่วนตัวไปนี่ค่อนข้่างลำบากพอสมควร ต้องเช่ามอไซต์ไป อันนี้ก็เช่าไปเหมือนกัน โดยผมเช่ามอไซต์ 1 วันวันละ 200 บาท (แต่มัดจำ 3000 บาท) ก็เอาเรื่องเหมือนกัน และก็มาเริ่มต้นที่ร้านแรกเลยคือ --- ### **Mr. A Coffee**  ร้านอาหารสไตล์บ้านๆ ที่ขายอาหาร น้ำ เครื่องดื่ม มีทั้งอาหารไทยและอาหารฝรั่ง ส่วนตัวก็ขับรถมอไซต์มายังสถานที่แห่งนี้ทางเข้าไปยังร้านเป็นหมู่บ้านเล็กๆ ไม่มีถนนเข้า แต่มอไซต์เข้าไปได้พอสมควร ตอนนั้นค่อนข้างเย็นมากแล้ว ได้มาสั่งอาหารมาคือ ข้าวเหนียวมะม่วงกับน้ำแก้วมังกรปั่นแบบไม่หวาน (ทั้งๆที่ตัวเองก็จะเตรียมไปกินบุ๊ปเฟ่อีกหนึ่งชั่วโมงข้างหน้า 555) ก็ได้สั่งไปแล้วก็ถามว่ารับ bitcoin ไหมครับ เจ้าของร้านก็บอกว่า รับๆ ผมกับเจ้าของร้านก็ได้พูดคุยกันเกือบประมาณครึ่งชั่วโมง ซึ่งหากผมมาเร็วกว่านี้หน่อยก็คงได้คุยกันยาวๆ แล้วละ ซึ่งเป็นการคุยที่สนุกมากซึ่งตัวเจ้าของร้านเองก็ได้เล่าถึงเหตุผลที่รับ bitcoin เหมือนกันว่าช่วง โควิดตอนปี 2020 ที่ผ่านมา บนเกาะช้างไม่มีอะไรเลยชาวบ้านก็ต้องไปหารากไม้ หาเห็ดตามป่าเขากัน แต่พี่เจ้าของร้านได้รู้จักกับฝรั่งคนหนึ่งเขาช่วยเหลือพี่เจ้าของร้านด้วยการบริจาคบิทคอยให้ และคนนี้ก็เป็นคนสอนให้เขารับบิทคอยโดยใช้ WOS และเจ้าของร้านก็เล่าให้ผมฟังเพิ่มเติม ณ ปัจจุบันว่า คนเราเองก็ยังต้องมีสภาพคล่องในการใช้งานอยู่ ตั้งมีเงิน fiat ไว้ส่วนหนึ่ง ส่วนบิทคอยที่ได้เขาได้ก็เก็บไว้เพื่อสร้างเป็นทรัพย์สินในอนาคตที่หากมีปัญหาช่วงไหนก็นำมาขายได้ ก็แลก P2P โดยตรง ซึ่งผมค่อนข้างตกใจเพราะเขาเรียนรู้จากการรับบิทคอยโดยนักท่องเที่ยวชาวต่างชาติที่ชวนเขาให้รับ เผื่อว่าจะมีฝรั่งมาใช้งานบิทคอย ณ สถานที่ร้านแห่งนี้  กึมมิคที่หลายท่านอาจจะต้องลุ้นหน่อยว่าหากมีโอกาสได้ไปเที่ยวและแวะที่ร้าน ก็คงต้่องลุ้นว่าคุณจะได้จ่ายด้วย bitcoin ไหม หากวันนั้นเจ้าของร้านไม่อยากรับเพราะว่าโคต้ารับบิทคอยวันนั้นเต็มแล้ว ฮ่าๆ รูปแบบระบบวาสนาร้านสูญของคุณมิกตอนเมื่อก่อน (เหมือนกันเลย) จริงๆ แล้วหากมีเวลามากพอก็คงได้พูดคุยกับพี่เจ้าของร้านสนุกๆกันไป ผมชอบความเรียบง่ายของร้านพี่เขา และมีอาหารหลากหลายอย่างเต็มไปหมด อีกเรื่องอย่างข้าวเหนียวมะม่วง ผมยังจำได้ว่าเมื่อก่อนมีแต่ช่วงฤดูเดียวที่สามารถกินมะม่วงสุกได้ หรือ อาหารแบบข้าวเหนียวมะม่วง แต่ปัจจุบันคือถ้าจะกิน ข้าวเหนียวมะม่วงแล้ว สามารถสั่งกินได้ตลอดทั้งปีกันเลยซึ่งก็โอเครพอสมควร แบบอยากไปทะเลตอนหน้าฝนแล้วอยากกินข้าวเหนียวมะม่วงของหน้าร้อนแบบนี้  ท้ายสุดร้าน Mr. A Coffee เป็นร้านที่ถ้านั่งชิวๆ แบบฝรั่งก็สามารถอยู่ได้ยาวๆ เลยนะจิบกาแฟ ทำงาน WFH ล้่อมรอบโดยธรรมชาติ แต่เส้นทางมาที่ร้านก็ลำบากหน่อยเหมาะกับคนที่ local จริงๆ low time ระดับหนึ่ง ท้ายสุดผมเองก็แจกสติกเกอร์ของพี่แชมป์เอาไปให้เจ้าของร้านแจกกันต่อไป  งานนี้ทั้งข้าวเหนียวมะม่วงและน้ำแก้วมังกรปั่น เสีย sats ไปทั้งหมด 6,050 sats แต่สิ่งที่ได้คือการแลกเปลี่ยนมุมมองกับเจ้าของร้านกับจุดเริ่มต้นของการรับบิทคอยในพื้นที่เกาะช้างแห่งนี้ และหากมีโอกาสอาจจะไปพักอยู่แถวนั้นชักอาทิตย์และแวะมาอุดหนุนร้านนี้ตลอด เพราะวิวฝั่งใต้สุดของเกาะช้างก็ยังคงความสวยงามไม่แพ้กับฝั่งทิศตะวันตกที่ฝรั่งอยู่กัน แต่ฝั่งใต้โซนนี้ก็มีความที่เป็นบ้านไม้ เพิงง่ายๆ ที่ชาวต่างชาติชอบกันอยู่ :) Google-map: https://maps.app.goo.gl/b45JGeTzL6Lwwi9i9 BTC-map: https://btcmap.org/merchant/node:12416107504 --- ### **Koh Chang Wine Gallery **  และเราก็ย้อนกลับมาอีกร้านหนึ่งในวันถัดไปและเป็นวันที่จะต้องออกจากเกาะช้างเช่นเดียวกัน และผมก็ไม่พลาดร้าน Koh Chang Wine Gallery ตั้งอยู่ในโซนหมู่บ้านแหล่งท่องเที่ยวเส้นทางถนนทางตะวันตก ร้านนี้ไม่ได้มีป้ายรับบิทคอย แต่รับชำระด้วยบิทคอยซึ่งเป็นฝรั่งท่านหนึ่งที่คาดว่าน่าจะแต่งงานกับภรรยาคนไทย เป็นร้านสไตล์แบบฝรั่งเลย ผมเองก็สั่งสเต็กเนื้อไป และน้ำมะม่วงปั่น (ไม่รู้เวลาไปเกาะทีไรติดใจกับน้ำมะม่วงปั่น) อาจจะไม่ได้พูดคุยอะไรมากมายนัก แต่ก็หมดไป 32,620 sats เป็นร้านอาหารเช้าและอาหารแนวฝรั่งตรงๆ ถือว่าค่อนข้างอร่อยใช้ได้ดีเลยทีเดียว แต่หากจะจ่ายด้วยบิทคอยก็ต้องแจ้งก่อนนะว่าขอจ่ายด้วยบิทคอยก่อน เหมือนพี่ฝรั่งที่เขารับตอนนี้ก็รับแต่เฉพาะ bitcoin อย่างเดียวเมื่อก่อนรับ xrp กับ doge ด้วยแต่ผมเองเวลาคุยกับฝรั่งก็เหงื่อแตกเหมือนกัน (รึว่าเพราะมันร้อน บนเกาะก็อบอ้าวใช้ได้ 555+)    Google-map: https://maps.app.goo.gl/6QbNgRbiV5Uao2Xz8 BTC-map: https://btcmap.org/merchant/node:11461720813 --- เส้นทางไปร้านค่อนข้างง่ายติดถนนในหมู่บ้าน ซึ่งหากมายังเกาะช้างแล้วหากขึ้นฝั่งมาแล้วเลี้ยวขวาก็จะขับรถหรือนั่งรถมาเส้นถนนฝั่งตะวันตกของเกาะก็จะพบกับร้านนี้ก่อน อันนี้แล้วแต่ความสะดวกแต่ละท่านเลยครับหากได้มีโอกาสแวะมาเกาะช้างและอยากใช้จ่าย bitcoin เราก็มีทางเลือกร้านในสองสไตล์กันเลย แบบวิถีฝรั่งตอนเช้าก็ร้าน Koh Chang Wine Gallery หรือ แบบ Local ก็ Mr. A Coffee หรือไปทังคู่เลยจะดีมากแต่ต้องบ้าหน่อย เพราะเส้นทางไปก็ค่อนข้างลำบากพอควรเหมือนกัน หมายถึงมีภูเขาชันมีทางขึ้นลงหักศอกนิดหน่อยก็เท่านั้นเอง รวมๆ ทริปบนเกาะช้างนี้ก็หมดไปไม่เยอะมาก 38,670 sats ก็จะตัวลอยเบาๆ หน่อย (สำรวจเมื่อ มีนาคม 2025 อนาคตอาจจะมีการเปลี่ยนแปลงได้) สำหรับจากนี้จะเป็นการ ปสก. ส่วนตัวกับการใช้งาน Bitcoin Lightning ตามสถานที่ที่ได้เดินทาง Part 3 จะเป็นสถานที่ในพื้นที่หาดใหญ่ จังหวัดสงขลา และ เสริมประสบการณ์การเดินทางโดยรถไฟระยะเวลาเกือบ 18 ชั่วโมง พร้อมด้วยมิตรสหายในรังอย่างกัปตัน จะป่วนแค่ไหนก็รอติดตามกันครับ :)
@ 0f9da413:01bd07d7
2025-04-03 05:32:55 หลังจากจบทริปเที่ยวพัทยาเรียบร้อยแล้วก็ได้เดินทางไปยังเกาะช้างโดยติดรถเจ้าหน้าที่ในที่ทำงานไปไปเกาะช้างครั้งแรกรู้สึกว่ามันไกลเหลือเกินไปค่อนข้างยากหากไม่มีรถส่วนตัว ถ้าให้ไปส่วนตัวก็คงต้องอยู่นานๆ หน่อยชักแบบอาทิตย์หนึ่ง ใช้ชีวิตแบบฝรั่งเที่ยวอยู่ง่ายๆ กินง่ายๆ จากที่ดูในแผนที่ btcmap แล้วพบว่าก็มีร้านที่ปักหมุดไว้อยู่ทั้งหมดสองร้านด้วยกันซึ่งระยะทางก็ค่อนข้างซันเหมือนกัน และมีเนินสูงต่ำสลับกันไป หากไม่มีรถส่วนตัวไปนี่ค่อนข้่างลำบากพอสมควร ต้องเช่ามอไซต์ไป อันนี้ก็เช่าไปเหมือนกัน โดยผมเช่ามอไซต์ 1 วันวันละ 200 บาท (แต่มัดจำ 3000 บาท) ก็เอาเรื่องเหมือนกัน และก็มาเริ่มต้นที่ร้านแรกเลยคือ --- ### **Mr. A Coffee**  ร้านอาหารสไตล์บ้านๆ ที่ขายอาหาร น้ำ เครื่องดื่ม มีทั้งอาหารไทยและอาหารฝรั่ง ส่วนตัวก็ขับรถมอไซต์มายังสถานที่แห่งนี้ทางเข้าไปยังร้านเป็นหมู่บ้านเล็กๆ ไม่มีถนนเข้า แต่มอไซต์เข้าไปได้พอสมควร ตอนนั้นค่อนข้างเย็นมากแล้ว ได้มาสั่งอาหารมาคือ ข้าวเหนียวมะม่วงกับน้ำแก้วมังกรปั่นแบบไม่หวาน (ทั้งๆที่ตัวเองก็จะเตรียมไปกินบุ๊ปเฟ่อีกหนึ่งชั่วโมงข้างหน้า 555) ก็ได้สั่งไปแล้วก็ถามว่ารับ bitcoin ไหมครับ เจ้าของร้านก็บอกว่า รับๆ ผมกับเจ้าของร้านก็ได้พูดคุยกันเกือบประมาณครึ่งชั่วโมง ซึ่งหากผมมาเร็วกว่านี้หน่อยก็คงได้คุยกันยาวๆ แล้วละ ซึ่งเป็นการคุยที่สนุกมากซึ่งตัวเจ้าของร้านเองก็ได้เล่าถึงเหตุผลที่รับ bitcoin เหมือนกันว่าช่วง โควิดตอนปี 2020 ที่ผ่านมา บนเกาะช้างไม่มีอะไรเลยชาวบ้านก็ต้องไปหารากไม้ หาเห็ดตามป่าเขากัน แต่พี่เจ้าของร้านได้รู้จักกับฝรั่งคนหนึ่งเขาช่วยเหลือพี่เจ้าของร้านด้วยการบริจาคบิทคอยให้ และคนนี้ก็เป็นคนสอนให้เขารับบิทคอยโดยใช้ WOS และเจ้าของร้านก็เล่าให้ผมฟังเพิ่มเติม ณ ปัจจุบันว่า คนเราเองก็ยังต้องมีสภาพคล่องในการใช้งานอยู่ ตั้งมีเงิน fiat ไว้ส่วนหนึ่ง ส่วนบิทคอยที่ได้เขาได้ก็เก็บไว้เพื่อสร้างเป็นทรัพย์สินในอนาคตที่หากมีปัญหาช่วงไหนก็นำมาขายได้ ก็แลก P2P โดยตรง ซึ่งผมค่อนข้างตกใจเพราะเขาเรียนรู้จากการรับบิทคอยโดยนักท่องเที่ยวชาวต่างชาติที่ชวนเขาให้รับ เผื่อว่าจะมีฝรั่งมาใช้งานบิทคอย ณ สถานที่ร้านแห่งนี้  กึมมิคที่หลายท่านอาจจะต้องลุ้นหน่อยว่าหากมีโอกาสได้ไปเที่ยวและแวะที่ร้าน ก็คงต้่องลุ้นว่าคุณจะได้จ่ายด้วย bitcoin ไหม หากวันนั้นเจ้าของร้านไม่อยากรับเพราะว่าโคต้ารับบิทคอยวันนั้นเต็มแล้ว ฮ่าๆ รูปแบบระบบวาสนาร้านสูญของคุณมิกตอนเมื่อก่อน (เหมือนกันเลย) จริงๆ แล้วหากมีเวลามากพอก็คงได้พูดคุยกับพี่เจ้าของร้านสนุกๆกันไป ผมชอบความเรียบง่ายของร้านพี่เขา และมีอาหารหลากหลายอย่างเต็มไปหมด อีกเรื่องอย่างข้าวเหนียวมะม่วง ผมยังจำได้ว่าเมื่อก่อนมีแต่ช่วงฤดูเดียวที่สามารถกินมะม่วงสุกได้ หรือ อาหารแบบข้าวเหนียวมะม่วง แต่ปัจจุบันคือถ้าจะกิน ข้าวเหนียวมะม่วงแล้ว สามารถสั่งกินได้ตลอดทั้งปีกันเลยซึ่งก็โอเครพอสมควร แบบอยากไปทะเลตอนหน้าฝนแล้วอยากกินข้าวเหนียวมะม่วงของหน้าร้อนแบบนี้  ท้ายสุดร้าน Mr. A Coffee เป็นร้านที่ถ้านั่งชิวๆ แบบฝรั่งก็สามารถอยู่ได้ยาวๆ เลยนะจิบกาแฟ ทำงาน WFH ล้่อมรอบโดยธรรมชาติ แต่เส้นทางมาที่ร้านก็ลำบากหน่อยเหมาะกับคนที่ local จริงๆ low time ระดับหนึ่ง ท้ายสุดผมเองก็แจกสติกเกอร์ของพี่แชมป์เอาไปให้เจ้าของร้านแจกกันต่อไป  งานนี้ทั้งข้าวเหนียวมะม่วงและน้ำแก้วมังกรปั่น เสีย sats ไปทั้งหมด 6,050 sats แต่สิ่งที่ได้คือการแลกเปลี่ยนมุมมองกับเจ้าของร้านกับจุดเริ่มต้นของการรับบิทคอยในพื้นที่เกาะช้างแห่งนี้ และหากมีโอกาสอาจจะไปพักอยู่แถวนั้นชักอาทิตย์และแวะมาอุดหนุนร้านนี้ตลอด เพราะวิวฝั่งใต้สุดของเกาะช้างก็ยังคงความสวยงามไม่แพ้กับฝั่งทิศตะวันตกที่ฝรั่งอยู่กัน แต่ฝั่งใต้โซนนี้ก็มีความที่เป็นบ้านไม้ เพิงง่ายๆ ที่ชาวต่างชาติชอบกันอยู่ :) Google-map: https://maps.app.goo.gl/b45JGeTzL6Lwwi9i9 BTC-map: https://btcmap.org/merchant/node:12416107504 --- ### **Koh Chang Wine Gallery **  และเราก็ย้อนกลับมาอีกร้านหนึ่งในวันถัดไปและเป็นวันที่จะต้องออกจากเกาะช้างเช่นเดียวกัน และผมก็ไม่พลาดร้าน Koh Chang Wine Gallery ตั้งอยู่ในโซนหมู่บ้านแหล่งท่องเที่ยวเส้นทางถนนทางตะวันตก ร้านนี้ไม่ได้มีป้ายรับบิทคอย แต่รับชำระด้วยบิทคอยซึ่งเป็นฝรั่งท่านหนึ่งที่คาดว่าน่าจะแต่งงานกับภรรยาคนไทย เป็นร้านสไตล์แบบฝรั่งเลย ผมเองก็สั่งสเต็กเนื้อไป และน้ำมะม่วงปั่น (ไม่รู้เวลาไปเกาะทีไรติดใจกับน้ำมะม่วงปั่น) อาจจะไม่ได้พูดคุยอะไรมากมายนัก แต่ก็หมดไป 32,620 sats เป็นร้านอาหารเช้าและอาหารแนวฝรั่งตรงๆ ถือว่าค่อนข้างอร่อยใช้ได้ดีเลยทีเดียว แต่หากจะจ่ายด้วยบิทคอยก็ต้องแจ้งก่อนนะว่าขอจ่ายด้วยบิทคอยก่อน เหมือนพี่ฝรั่งที่เขารับตอนนี้ก็รับแต่เฉพาะ bitcoin อย่างเดียวเมื่อก่อนรับ xrp กับ doge ด้วยแต่ผมเองเวลาคุยกับฝรั่งก็เหงื่อแตกเหมือนกัน (รึว่าเพราะมันร้อน บนเกาะก็อบอ้าวใช้ได้ 555+)    Google-map: https://maps.app.goo.gl/6QbNgRbiV5Uao2Xz8 BTC-map: https://btcmap.org/merchant/node:11461720813 --- เส้นทางไปร้านค่อนข้างง่ายติดถนนในหมู่บ้าน ซึ่งหากมายังเกาะช้างแล้วหากขึ้นฝั่งมาแล้วเลี้ยวขวาก็จะขับรถหรือนั่งรถมาเส้นถนนฝั่งตะวันตกของเกาะก็จะพบกับร้านนี้ก่อน อันนี้แล้วแต่ความสะดวกแต่ละท่านเลยครับหากได้มีโอกาสแวะมาเกาะช้างและอยากใช้จ่าย bitcoin เราก็มีทางเลือกร้านในสองสไตล์กันเลย แบบวิถีฝรั่งตอนเช้าก็ร้าน Koh Chang Wine Gallery หรือ แบบ Local ก็ Mr. A Coffee หรือไปทังคู่เลยจะดีมากแต่ต้องบ้าหน่อย เพราะเส้นทางไปก็ค่อนข้างลำบากพอควรเหมือนกัน หมายถึงมีภูเขาชันมีทางขึ้นลงหักศอกนิดหน่อยก็เท่านั้นเอง รวมๆ ทริปบนเกาะช้างนี้ก็หมดไปไม่เยอะมาก 38,670 sats ก็จะตัวลอยเบาๆ หน่อย (สำรวจเมื่อ มีนาคม 2025 อนาคตอาจจะมีการเปลี่ยนแปลงได้) สำหรับจากนี้จะเป็นการ ปสก. ส่วนตัวกับการใช้งาน Bitcoin Lightning ตามสถานที่ที่ได้เดินทาง Part 3 จะเป็นสถานที่ในพื้นที่หาดใหญ่ จังหวัดสงขลา และ เสริมประสบการณ์การเดินทางโดยรถไฟระยะเวลาเกือบ 18 ชั่วโมง พร้อมด้วยมิตรสหายในรังอย่างกัปตัน จะป่วนแค่ไหนก็รอติดตามกันครับ :) @ d5c3d063:4d1159b3
2025-04-03 04:09:56### ทรัมป์ ขึ้นภาษีนำเข้า สิ่งที่คุณเห็น…กับสิ่งที่คุณมองไม่เห็น คุณ #เห็น แค่ฝั่งที่ดูดีในข่าวภาคค่ำ แต่คุณ #ไม่เห็น – คนทั้งประเทศ ต้องจ่ายของแพงขึ้น – ธุรกิจเล็ก ๆ ที่พึ่งการนำเข้า…ถูกบีบให้ตาย – ผู้บริโภคต้องเสียเงินมากขึ้น โดยไม่มีทางเลือก รัฐอ้างว่า *"ปกป้องประเทศ"* แต่จริง ๆ แล้วเขาแค่ โยนภาระให้คนส่วนใหญ่ เพื่ออุ้มผลประโยชน์บางกลุ่ม เหมือนที่ Bastiat เรียกว่า *“การปล้นที่ถูกกฎหมาย”* Hazlitt ขยายต่อใน Economics in One Lesson ว่า > เศรษฐศาสตร์ที่ดี ต้องมองให้พ้นจากผลเฉพาะหน้า > และมองให้เห็นผลกระทบต่อทุกคน ไม่ใช่แค่บางกลุ่ม เงินเฟ้อ คือการขโมยแบบเงียบ ๆ ภาษีศุลกากร คือการปล้นอย่างเปิดเผย วันนี้ #EIOL น่าจะถึงมือเพื่อนๆ หลายคนแล้ว เล่มนี้ไม่ต้องอ่านทีละบทก็ได้ ลองเปิดไปบทที่ 11 เลยแล้วจะเจอ**ค้อนปอน**สำหรับทุบมายาคดีทางเศรษฐกิจที่รัฐใช้กับเรามาทั้งชีวิต อ่าน #เศรษฐศาสตร์เล่มเดียวจบ แล้วคุณอาจไม่มีวันมอง “นโยบายเพื่อประชาชน” ได้เหมือนเดิมอีก เพราะบางที...สิ่งที่คุณไม่เคยเห็น อาจเป็นสิ่งที่คุณควรรู้(เห็น)ให้เร็วที่สุด #Siamstr
@ d5c3d063:4d1159b3
2025-04-03 04:09:56### ทรัมป์ ขึ้นภาษีนำเข้า สิ่งที่คุณเห็น…กับสิ่งที่คุณมองไม่เห็น คุณ #เห็น แค่ฝั่งที่ดูดีในข่าวภาคค่ำ แต่คุณ #ไม่เห็น – คนทั้งประเทศ ต้องจ่ายของแพงขึ้น – ธุรกิจเล็ก ๆ ที่พึ่งการนำเข้า…ถูกบีบให้ตาย – ผู้บริโภคต้องเสียเงินมากขึ้น โดยไม่มีทางเลือก รัฐอ้างว่า *"ปกป้องประเทศ"* แต่จริง ๆ แล้วเขาแค่ โยนภาระให้คนส่วนใหญ่ เพื่ออุ้มผลประโยชน์บางกลุ่ม เหมือนที่ Bastiat เรียกว่า *“การปล้นที่ถูกกฎหมาย”* Hazlitt ขยายต่อใน Economics in One Lesson ว่า > เศรษฐศาสตร์ที่ดี ต้องมองให้พ้นจากผลเฉพาะหน้า > และมองให้เห็นผลกระทบต่อทุกคน ไม่ใช่แค่บางกลุ่ม เงินเฟ้อ คือการขโมยแบบเงียบ ๆ ภาษีศุลกากร คือการปล้นอย่างเปิดเผย วันนี้ #EIOL น่าจะถึงมือเพื่อนๆ หลายคนแล้ว เล่มนี้ไม่ต้องอ่านทีละบทก็ได้ ลองเปิดไปบทที่ 11 เลยแล้วจะเจอ**ค้อนปอน**สำหรับทุบมายาคดีทางเศรษฐกิจที่รัฐใช้กับเรามาทั้งชีวิต อ่าน #เศรษฐศาสตร์เล่มเดียวจบ แล้วคุณอาจไม่มีวันมอง “นโยบายเพื่อประชาชน” ได้เหมือนเดิมอีก เพราะบางที...สิ่งที่คุณไม่เคยเห็น อาจเป็นสิ่งที่คุณควรรู้(เห็น)ให้เร็วที่สุด #Siamstr @ 378562cd:a6fc6773
2025-04-02 22:41:57Nostr is a decentralized, censorship-resistant social media protocol designed to give users control over online interactions without relying on central authorities. While its architecture offers notable advantages, it also introduces challenges, particularly concerning user anonymity, content moderation, and the dynamics of user influence. Anonymity and the Risk of Bullying Nostr's design allows users to create identities without traditional verification methods like email addresses or phone numbers. Instead, users generate a cryptographic key pair: a public key serving as their identifier and a private key for signing messages. This approach enhances privacy but can lead to the "online disinhibition effect," where individuals feel less accountable for their actions due to perceived anonymity. This phenomenon has been linked to increased instances of cyberbullying, as users may engage in behavior online that they would avoid in face-to-face interactions. Influence Disparities Among Users In decentralized networks like Nostr, users with larger followings can have a more extensive reach, amplifying their messages across the network. This can create disparities where individuals with thousands of followers wield more influence than those with fewer connections. While this dynamic is not unique to Nostr, the protocol's structure may exacerbate the visibility gap between highly followed users and those with a smaller audience. Content Moderation and the Challenge of Deletion Due to Nostr's decentralized nature, content moderation and deletion present significant challenges. Removing content to multiple relays becomes complex once a user posts content to multiple relays, as each relay operates independently. Unlike centralized platforms where a post can be deleted universally, Nostr's architecture means that deleting a post from one relay doesn't ensure its removal from others. This persistence underscores the importance of thoughtful posting, as content may remain accessible indefinitely. Mitigation Strategies and User Empowerment Despite these challenges, Nostr offers mechanisms to empower users to manage their experience. Clients can implement features allowing users to mute or block others, tailoring their interactions and content exposure. Additionally, some clients support user-led moderation, enabling individuals to label content as offensive or inappropriate, contributing to a community-driven approach to content management. In summary, while Nostr's decentralized and anonymous framework promotes freedom and resistance to censorship, it also necessitates a proactive approach from users to navigate challenges related to anonymity, influence disparities, and content permanence. As the platform evolves, ongoing development and community engagement will be crucial in addressing these issues to foster a safe and equitable environment for all participants.
@ 378562cd:a6fc6773
2025-04-02 22:41:57Nostr is a decentralized, censorship-resistant social media protocol designed to give users control over online interactions without relying on central authorities. While its architecture offers notable advantages, it also introduces challenges, particularly concerning user anonymity, content moderation, and the dynamics of user influence. Anonymity and the Risk of Bullying Nostr's design allows users to create identities without traditional verification methods like email addresses or phone numbers. Instead, users generate a cryptographic key pair: a public key serving as their identifier and a private key for signing messages. This approach enhances privacy but can lead to the "online disinhibition effect," where individuals feel less accountable for their actions due to perceived anonymity. This phenomenon has been linked to increased instances of cyberbullying, as users may engage in behavior online that they would avoid in face-to-face interactions. Influence Disparities Among Users In decentralized networks like Nostr, users with larger followings can have a more extensive reach, amplifying their messages across the network. This can create disparities where individuals with thousands of followers wield more influence than those with fewer connections. While this dynamic is not unique to Nostr, the protocol's structure may exacerbate the visibility gap between highly followed users and those with a smaller audience. Content Moderation and the Challenge of Deletion Due to Nostr's decentralized nature, content moderation and deletion present significant challenges. Removing content to multiple relays becomes complex once a user posts content to multiple relays, as each relay operates independently. Unlike centralized platforms where a post can be deleted universally, Nostr's architecture means that deleting a post from one relay doesn't ensure its removal from others. This persistence underscores the importance of thoughtful posting, as content may remain accessible indefinitely. Mitigation Strategies and User Empowerment Despite these challenges, Nostr offers mechanisms to empower users to manage their experience. Clients can implement features allowing users to mute or block others, tailoring their interactions and content exposure. Additionally, some clients support user-led moderation, enabling individuals to label content as offensive or inappropriate, contributing to a community-driven approach to content management. In summary, while Nostr's decentralized and anonymous framework promotes freedom and resistance to censorship, it also necessitates a proactive approach from users to navigate challenges related to anonymity, influence disparities, and content permanence. As the platform evolves, ongoing development and community engagement will be crucial in addressing these issues to foster a safe and equitable environment for all participants. @ 3c7dc2c5:805642a8
2025-04-02 21:15:55## 🧠Quote(s) of the week: CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs. ## 🧡Bitcoin news🧡 2025 https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg On the 24th of March: ➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity. ➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion). Look at the corporate Bitcoin ownership breakdown: - MicroStrategy: 506,000+ BTC - Marathon: ~46,000 BTC (10x smaller) - Riot: ~19,000 BTC (26x smaller) That acquisition curve has gone parabolic since Q4 2024. Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale. Clear institutional conviction signal here.' -Ecoinometrics ➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine." On the 25th of March: ➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL - This is one of the most reliable "buy" indicators. - Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive (foto) Bitcoin is always a buy. Just DCA. ➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest. ➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin. ➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world. Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives) But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.' ➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization". I rather believe the opposite. Under Femke Halsema - Amsterdam - The number of civil servants increased by 50% (14K -> 20K) - Debt increased by 150% (4 billion -> approx. 10 billion) Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity. Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better. ➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment. ➡️BlackRock launched a European Bitcoin ETP today - Bloomberg ➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin. On the 26th of March: ➡️NYDIG just became a big Bitcoin miner. Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG. ➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds. ➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest. That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds. ➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses. ➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD. → Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin → Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin → Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time. Source: https://t.co/QDj61ZDe6O The Blockchain Group is Europe's First Bitcoin Treasury Company! On the 27th of March: ➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard ➡️Daniel Batten: Yet another paper on Bitcoin and energy TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition are greater than generally assumed" The journal has a (high) impact factor of 7.1." Source: https://t.co/W3gytMgcpC ➡️A home miner with only 4 machines mined block 888737. https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg Bitcoin proves anyone can participate and earn—true freedom! ➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks. 200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News ➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025. On the 28th of March: ➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today. ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes! ➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina. ➡️A Russian company built a Bitcoin mine in the Arctic. Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs. ➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity. https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg another great chart: https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg On the 29th of March: ➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin. https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png ➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill. If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use. ➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207. On the 31st of March: ➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders: “If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin." https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf ➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin. ➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds. ➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem. A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia. Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening. https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg On the 1st of April: ➡️'Over 73,353 BTC were bought by corporations in Q1 2025. Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now... Which company do you want to see adopt BTC next?' Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723 ➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC. On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC. ➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish ➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county. ➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide. Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.' ## 💸Traditional Finance / Macro: On the 29th of March 👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION. Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL ## 🏦Banks: 👉🏽 no news ## 🌎Macro/Geopolitics: On the 24th of March: 👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history. Every time it crossed this level it marked the beginning of an 18-month recession/depression. 1929, 1973, 2008 & 2025' I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both. 👉🏽US household wealth is falling: US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates. By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion. In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback. Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks. This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures. Consumer spending is set to slow in Q2 2025.' -TKL 👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes. BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left." Today, the 27th of March, marks those 1,028 days, and nothing happened. Climate doomers are like Aztecs who think the sun stops unless they cut out some organs." 👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today. For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/ They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe. On the 25th of March: 👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though. 👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse. The Green Deal is moving full speed ahead—soon everyone will be relying on food banks… For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen On the 26th of March: 👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all. Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening. On the 27th of March: 👉🏽Gold surpasses $3,100 for the first time in history. TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years. This is also the 3rd-longest streak on record after a historic run during the late 1970s. The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation. As a result, gold prices recorded 4 consecutive yearly gains.' On the 31st of March for the first time, gold blasted through $100,000/kilogram. This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.' 👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come. On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored." On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over." That is the Mark I know! "Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.” On the 28th of March: 👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993. Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed. Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction. It’s negative even “gold adjusted” 4 weeks ago it was +2.3% 8 weeks ago it was +3.9% Yikes! 👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure. The remaining 900 employees are set to be terminated. 👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei 👉🏽Fix the money, fix the world: DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government” “It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account” “We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION” “There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit” Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe. On the 29th of March: 👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion. Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge On the 1st of April: In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week: https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros. Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!? For our own housing market? “Too political.” For war and Brussels' military ambitions? €100,000,000,000—no problem. They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda. Got Bitcoin? I will end this Weekly Recap with a Stanley Druckenmiller quote: "My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully." "I tend to think that's what great investors do." I know what I do and have. Bitcoin! ## 🎁If you have made it this far I would like to give you a little gift: What Bitcoin Did: Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy. https://www.youtube.com/watch?v=_bSprc0IAow Credit: I have used multiple sources! My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly. `Use the code SE3997` Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀ ⠀⠀ ⠀ ⠀⠀⠀ Do you think this post is helpful to you? If so, please share it and support my work with a zap. ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ ⭐ Many thanks⭐ Felipe - Bitcoin Friday! ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
@ 3c7dc2c5:805642a8
2025-04-02 21:15:55## 🧠Quote(s) of the week: CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs. ## 🧡Bitcoin news🧡 2025 https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg On the 24th of March: ➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity. ➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion). Look at the corporate Bitcoin ownership breakdown: - MicroStrategy: 506,000+ BTC - Marathon: ~46,000 BTC (10x smaller) - Riot: ~19,000 BTC (26x smaller) That acquisition curve has gone parabolic since Q4 2024. Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale. Clear institutional conviction signal here.' -Ecoinometrics ➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine." On the 25th of March: ➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL - This is one of the most reliable "buy" indicators. - Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive (foto) Bitcoin is always a buy. Just DCA. ➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest. ➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin. ➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world. Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives) But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.' ➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization". I rather believe the opposite. Under Femke Halsema - Amsterdam - The number of civil servants increased by 50% (14K -> 20K) - Debt increased by 150% (4 billion -> approx. 10 billion) Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity. Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better. ➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment. ➡️BlackRock launched a European Bitcoin ETP today - Bloomberg ➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin. On the 26th of March: ➡️NYDIG just became a big Bitcoin miner. Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG. ➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds. ➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest. That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds. ➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses. ➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD. → Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin → Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin → Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time. Source: https://t.co/QDj61ZDe6O The Blockchain Group is Europe's First Bitcoin Treasury Company! On the 27th of March: ➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard ➡️Daniel Batten: Yet another paper on Bitcoin and energy TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition are greater than generally assumed" The journal has a (high) impact factor of 7.1." Source: https://t.co/W3gytMgcpC ➡️A home miner with only 4 machines mined block 888737. https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg Bitcoin proves anyone can participate and earn—true freedom! ➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks. 200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News ➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025. On the 28th of March: ➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today. ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes! ➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina. ➡️A Russian company built a Bitcoin mine in the Arctic. Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs. ➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity. https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg another great chart: https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg On the 29th of March: ➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin. https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png ➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill. If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use. ➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207. On the 31st of March: ➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders: “If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin." https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf ➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin. ➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds. ➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem. A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia. Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening. https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg On the 1st of April: ➡️'Over 73,353 BTC were bought by corporations in Q1 2025. Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now... Which company do you want to see adopt BTC next?' Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723 ➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC. On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC. ➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish ➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county. ➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide. Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.' ## 💸Traditional Finance / Macro: On the 29th of March 👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION. Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL ## 🏦Banks: 👉🏽 no news ## 🌎Macro/Geopolitics: On the 24th of March: 👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history. Every time it crossed this level it marked the beginning of an 18-month recession/depression. 1929, 1973, 2008 & 2025' I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both. 👉🏽US household wealth is falling: US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates. By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion. In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback. Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks. This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures. Consumer spending is set to slow in Q2 2025.' -TKL 👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes. BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left." Today, the 27th of March, marks those 1,028 days, and nothing happened. Climate doomers are like Aztecs who think the sun stops unless they cut out some organs." 👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today. For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/ They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe. On the 25th of March: 👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though. 👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse. The Green Deal is moving full speed ahead—soon everyone will be relying on food banks… For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen On the 26th of March: 👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all. Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening. On the 27th of March: 👉🏽Gold surpasses $3,100 for the first time in history. TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years. This is also the 3rd-longest streak on record after a historic run during the late 1970s. The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation. As a result, gold prices recorded 4 consecutive yearly gains.' On the 31st of March for the first time, gold blasted through $100,000/kilogram. This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.' 👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come. On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored." On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over." That is the Mark I know! "Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.” On the 28th of March: 👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993. Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed. Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction. It’s negative even “gold adjusted” 4 weeks ago it was +2.3% 8 weeks ago it was +3.9% Yikes! 👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure. The remaining 900 employees are set to be terminated. 👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei 👉🏽Fix the money, fix the world: DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government” “It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account” “We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION” “There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit” Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe. On the 29th of March: 👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion. Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge On the 1st of April: In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week: https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros. Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!? For our own housing market? “Too political.” For war and Brussels' military ambitions? €100,000,000,000—no problem. They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda. Got Bitcoin? I will end this Weekly Recap with a Stanley Druckenmiller quote: "My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully." "I tend to think that's what great investors do." I know what I do and have. Bitcoin! ## 🎁If you have made it this far I would like to give you a little gift: What Bitcoin Did: Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy. https://www.youtube.com/watch?v=_bSprc0IAow Credit: I have used multiple sources! My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly. `Use the code SE3997` Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀ ⠀⠀ ⠀ ⠀⠀⠀ Do you think this post is helpful to you? If so, please share it and support my work with a zap. ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ ⭐ Many thanks⭐ Felipe - Bitcoin Friday! ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ @ ef53426a:7e988851
2025-04-02 21:02:06# Bartering and early money \ Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align. Enter money. It’s used as an indirect exchange for any goods, so everyone wants it. Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services. As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money. --- # Gold — the basis for sound money \ Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining). Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something. Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money. --- # Currencies devalued \ Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire. The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold. In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned. --- # Government-backed money \ Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies. By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate. The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold. --- # Sound money = functioning economy \ Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future. The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events. --- # Recessions and debt arise from unsound money \ Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles. According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt. We need to return to sound money and a new gold standard. Enter bitcoin. --- # Bitcoin is scarce \ Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued. The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward. Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released. That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value. --- # Bitcoin is secure \ The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information. Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power. Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value. --- # Challenges for adoption \ Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value. Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended. Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system. ---  This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading). ‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018. Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop)
@ ef53426a:7e988851
2025-04-02 21:02:06# Bartering and early money \ Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align. Enter money. It’s used as an indirect exchange for any goods, so everyone wants it. Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services. As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money. --- # Gold — the basis for sound money \ Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining). Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something. Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money. --- # Currencies devalued \ Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire. The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold. In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned. --- # Government-backed money \ Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies. By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate. The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold. --- # Sound money = functioning economy \ Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future. The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events. --- # Recessions and debt arise from unsound money \ Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles. According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt. We need to return to sound money and a new gold standard. Enter bitcoin. --- # Bitcoin is scarce \ Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued. The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward. Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released. That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value. --- # Bitcoin is secure \ The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information. Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power. Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value. --- # Challenges for adoption \ Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value. Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended. Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system. ---  This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading). ‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018. Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop) @ 7d33ba57:1b82db35
2025-04-02 19:47:25Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.  ## **🏛️ Top Things to See & Do in Trogir** ### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡** - Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**. - Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**. - Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**. ### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪** - Offers **stunning panoramic views** over Trogir and the Adriatic. - A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery! ### **3️⃣ Visit Kamerlengo Fortress 🏰** - A **15th-century Venetian fortress** with **amazing sea views** from the top. - In summer, it hosts **concerts and cultural events**. ### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊** - A lively waterfront filled with **cafés, restaurants, and luxury yachts**. - Perfect for a **relaxing evening walk** while watching the sunset.  ### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️** - **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities. - **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**. - **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation. ### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️** - A **stunning turquoise bay**, perfect for **swimming and snorkeling**. - Just **a short boat ride from Trogir**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟 - **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi. - **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.  ## **🚗 How to Get to Trogir** ✈️ **By Air:** - **Split Airport (SPU)** is just **10 minutes away**! 🚕 🚘 **By Car:** - **From Split:** ~30 minutes (27 km) - **From Zadar:** ~1.5 hours (130 km) 🚌 **By Bus:** Frequent buses run between **Split and Trogir**. ⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.  ## **💡 Tips for Visiting Trogir** ✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️ ✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅 ✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟 ✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤 ✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷 
@ 7d33ba57:1b82db35
2025-04-02 19:47:25Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.  ## **🏛️ Top Things to See & Do in Trogir** ### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡** - Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**. - Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**. - Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**. ### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪** - Offers **stunning panoramic views** over Trogir and the Adriatic. - A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery! ### **3️⃣ Visit Kamerlengo Fortress 🏰** - A **15th-century Venetian fortress** with **amazing sea views** from the top. - In summer, it hosts **concerts and cultural events**. ### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊** - A lively waterfront filled with **cafés, restaurants, and luxury yachts**. - Perfect for a **relaxing evening walk** while watching the sunset.  ### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️** - **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities. - **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**. - **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation. ### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️** - A **stunning turquoise bay**, perfect for **swimming and snorkeling**. - Just **a short boat ride from Trogir**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟 - **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi. - **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.  ## **🚗 How to Get to Trogir** ✈️ **By Air:** - **Split Airport (SPU)** is just **10 minutes away**! 🚕 🚘 **By Car:** - **From Split:** ~30 minutes (27 km) - **From Zadar:** ~1.5 hours (130 km) 🚌 **By Bus:** Frequent buses run between **Split and Trogir**. ⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.  ## **💡 Tips for Visiting Trogir** ✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️ ✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅 ✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟 ✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤 ✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷  @ cbaa0c82:e9313245
2025-04-02 18:53:57#TheWholeGrain - #March2025 March of 2025 was a standard month for Bread and Toast. However, it did include a the occasional five Sunday Singles which seems like hitting the jackpot! Talk about lucky! Included with the five Sunday Singles was two more pages of the Adventure Series: Questline where we saw Bread, Toast, and End-Piece face off against their first adversary! End-Piece made a first appearance for in Toast's Comic Collection under the title E: The Last Slice while the Concept Art piece was the original drawing of all three slices of bread together. And, last of all we updated the Bitcoin logo because why not!? **Sunday Singles - March 2025** 2025-03-02 | Sunday Single 82 Title: Slingshot! *Watch out! Toast is quite the sharpshooter!* https://i.nostr.build/zHA9C7cOOZLOCl0o.png 2025-03-09 | Sunday Single 83 Title: Puzzles *End-Piece just figured out the puzzle!* https://i.nostr.build/u2EBdcsuwO2xo23P.png 2025-03-16 | Sunday Single 84 Title: Basketball *Oh, the madness!* https://i.nostr.build/8F1OFFVra7zQOIy6.png 2025-03-23 | Sunday Single 85 Title: Coffee *The perfect way to start the day.* https://i.nostr.build/aiGZOvOmow3igru6.png 2025-03-30 | Sunday Single 86 Title: Origami *End-Piece has a way with paper.* https://i.nostr.build/0ySzGwF9QnZxwLxD.png **Adventure Series: Questline** The group is attacked by a crow with Bread being the target of the giant bird, but with a group of trusty friends any enemy can be defeated! Artist: Dakota Jernigan (The Bitcoin Painter) Writer: Daniel David (dan 🍞) 2025-03-11 | Questline 005 - Under Attack *Toast and End-Piece are able to escape the attack from the giant winged predator, but Bread being distracted by thoughts of the village is caught off guard. End-Piece immediately charges the attacker with a fury of mallet swings. Meanwhile, Toast loads up an arrow with intentions of piercing through the giant bird.* https://i.nostr.build/F24sd7SFFbsW9WZY.png 2025-03-25 | Questline 006 - A Finished Battle *End-Piece lands a series of blows to the winged beast. Toast finishes it off with a second arrow to the heart. Bread is only slightly injured, but is more upset about having been so vulnerable due to being so distracted. Moving forward Bread will have to be more vigilant.* https://i.nostr.build/n5a7Jztq9MHxuGNf.png **Other Content Released in March 2025** 2025-03-05 | Toast's Comic Collection Title: E: The Last Slice #11 *A gluten-based pandemic has killed off all slices of bread that are not Toast except for one slice of bread that happens to be an end piece.* https://i.nostr.build/aar20oHAAKmZOovD.png 2025-03-12 | Concept Art Title: Original Bread and Toast *This was the first drawing of all three characters together. It was used a lot for branding when the project first started up in 2023.* https://i.nostr.build/yqkmBuTiH8AKbCzI.png 2025-03-19 | Bitcoin Art Title: Bitcoin/Bread Block Height: 888566 *Two things that just go together.* https://i.nostr.build/MDPkzOPVEaOJVTFE.png Thanks for checking out the seventh issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com! **So long, March!** ***Bread, Toast, and End-Piece*** #BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #🍞 #🖼️ ***List of nPubs Mentioned:*** The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g dan 🍞: npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6
@ cbaa0c82:e9313245
2025-04-02 18:53:57#TheWholeGrain - #March2025 March of 2025 was a standard month for Bread and Toast. However, it did include a the occasional five Sunday Singles which seems like hitting the jackpot! Talk about lucky! Included with the five Sunday Singles was two more pages of the Adventure Series: Questline where we saw Bread, Toast, and End-Piece face off against their first adversary! End-Piece made a first appearance for in Toast's Comic Collection under the title E: The Last Slice while the Concept Art piece was the original drawing of all three slices of bread together. And, last of all we updated the Bitcoin logo because why not!? **Sunday Singles - March 2025** 2025-03-02 | Sunday Single 82 Title: Slingshot! *Watch out! Toast is quite the sharpshooter!* https://i.nostr.build/zHA9C7cOOZLOCl0o.png 2025-03-09 | Sunday Single 83 Title: Puzzles *End-Piece just figured out the puzzle!* https://i.nostr.build/u2EBdcsuwO2xo23P.png 2025-03-16 | Sunday Single 84 Title: Basketball *Oh, the madness!* https://i.nostr.build/8F1OFFVra7zQOIy6.png 2025-03-23 | Sunday Single 85 Title: Coffee *The perfect way to start the day.* https://i.nostr.build/aiGZOvOmow3igru6.png 2025-03-30 | Sunday Single 86 Title: Origami *End-Piece has a way with paper.* https://i.nostr.build/0ySzGwF9QnZxwLxD.png **Adventure Series: Questline** The group is attacked by a crow with Bread being the target of the giant bird, but with a group of trusty friends any enemy can be defeated! Artist: Dakota Jernigan (The Bitcoin Painter) Writer: Daniel David (dan 🍞) 2025-03-11 | Questline 005 - Under Attack *Toast and End-Piece are able to escape the attack from the giant winged predator, but Bread being distracted by thoughts of the village is caught off guard. End-Piece immediately charges the attacker with a fury of mallet swings. Meanwhile, Toast loads up an arrow with intentions of piercing through the giant bird.* https://i.nostr.build/F24sd7SFFbsW9WZY.png 2025-03-25 | Questline 006 - A Finished Battle *End-Piece lands a series of blows to the winged beast. Toast finishes it off with a second arrow to the heart. Bread is only slightly injured, but is more upset about having been so vulnerable due to being so distracted. Moving forward Bread will have to be more vigilant.* https://i.nostr.build/n5a7Jztq9MHxuGNf.png **Other Content Released in March 2025** 2025-03-05 | Toast's Comic Collection Title: E: The Last Slice #11 *A gluten-based pandemic has killed off all slices of bread that are not Toast except for one slice of bread that happens to be an end piece.* https://i.nostr.build/aar20oHAAKmZOovD.png 2025-03-12 | Concept Art Title: Original Bread and Toast *This was the first drawing of all three characters together. It was used a lot for branding when the project first started up in 2023.* https://i.nostr.build/yqkmBuTiH8AKbCzI.png 2025-03-19 | Bitcoin Art Title: Bitcoin/Bread Block Height: 888566 *Two things that just go together.* https://i.nostr.build/MDPkzOPVEaOJVTFE.png Thanks for checking out the seventh issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com! **So long, March!** ***Bread, Toast, and End-Piece*** #BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #🍞 #🖼️ ***List of nPubs Mentioned:*** The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g dan 🍞: npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6 @ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher
@ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher @ 8d34bd24:414be32b
2025-04-02 14:13:03I was reading this passage last night: > …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine} Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself. This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation. > And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28) When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect: > And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine} When one particular man said that he would follow Jesus anywhere, Jesus responded this way. > As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine} Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort. > “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine} Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect. > “**For my thoughts are not your thoughts,\ > neither are your ways my ways**,”\ > declares the Lord. > > “As the heavens are higher than the earth,\ > so are **my ways higher than your ways**\ > and my thoughts than your thoughts. > > As the rain and the snow\ > come down from heaven,\ > and do not return to it\ > without watering the earth\ > and making it bud and flourish,\ > so that it yields seed for the sower and bread for the eater,\ > so is **my word that goes out from my mouth:\ > It will not return to me empty,\ > but will accomplish what I desire\ > and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine} God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us. > Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine} In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word. > They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine} Peter specifically warns believers to expect trials and hardship. > Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And, > > “If it is hard for the righteous to be saved,\ > what will become of the ungodly and the sinner?” > > So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine} Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship. > …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine} No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good. > Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written, > > “For Your sake we are being put to death all day long;\ > We were considered as sheep to be slaughtered.” > ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine} I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be. First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard. Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion. In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before. When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good. We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness. > Oh, the depth of the riches of the wisdom and knowledge of God!\ > How unsearchable his judgments,\ > and his paths beyond tracing out!\ > “Who has known the mind of the Lord?\ > Or who has been his counselor?”\ > “Who has ever given to God,\ > that God should repay them?”\ > For from him and through him and for him are all things.\ > To him be the glory forever! Amen. (Romans 11:33-36) Trust Jesus
@ 8d34bd24:414be32b
2025-04-02 14:13:03I was reading this passage last night: > …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine} Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself. This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation. > And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28) When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect: > And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine} When one particular man said that he would follow Jesus anywhere, Jesus responded this way. > As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine} Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort. > “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine} Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect. > “**For my thoughts are not your thoughts,\ > neither are your ways my ways**,”\ > declares the Lord. > > “As the heavens are higher than the earth,\ > so are **my ways higher than your ways**\ > and my thoughts than your thoughts. > > As the rain and the snow\ > come down from heaven,\ > and do not return to it\ > without watering the earth\ > and making it bud and flourish,\ > so that it yields seed for the sower and bread for the eater,\ > so is **my word that goes out from my mouth:\ > It will not return to me empty,\ > but will accomplish what I desire\ > and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine} God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us. > Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine} In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word. > They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine} Peter specifically warns believers to expect trials and hardship. > Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And, > > “If it is hard for the righteous to be saved,\ > what will become of the ungodly and the sinner?” > > So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine} Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship. > …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine} No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good. > Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written, > > “For Your sake we are being put to death all day long;\ > We were considered as sheep to be slaughtered.” > ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine} I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be. First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard. Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion. In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before. When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good. We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness. > Oh, the depth of the riches of the wisdom and knowledge of God!\ > How unsearchable his judgments,\ > and his paths beyond tracing out!\ > “Who has known the mind of the Lord?\ > Or who has been his counselor?”\ > “Who has ever given to God,\ > that God should repay them?”\ > For from him and through him and for him are all things.\ > To him be the glory forever! Amen. (Romans 11:33-36) Trust Jesus @ f3873798:24b3f2f3
2025-04-02 13:50:17O Bitcoin e as criptomoedas surgiram como uma alternativa descentralizada ao sistema financeiro tradicional. No entanto, no Brasil, o **Sistema Financeiro Nacional (SFN)** tem adotado medidas para controlar e limitar a exposição de investidores e instituições a esses ativos. Neste artigo, exploraremos as principais resoluções e regulamentações que restringem o investimento em Bitcoin no país. ## **O Posicionamento do Banco Central do Brasil (Bacen)**  O Banco Central do Brasil (Bacen) e outros órgãos reguladores, como a **Comissão de Valores Mobiliários (CVM)**, têm adotado uma postura cautelosa em relação às criptomoedas. ### **Resolução Bacen nº 4.753/2021** - Proíbe que instituições financeiras ofereçam serviços de criptomoedas em suas carteiras sem autorização prévia. - Restringe bancos e corretoras de operarem diretamente com criptoativos, limitando sua integração ao sistema financeiro tradicional. ### **Comunicado do Bacen sobre Riscos das Criptomoedas** - O Bacen já emitiu alertas sobre os riscos de volatilidade, fraudes e falta de garantias em investimentos em Bitcoin. - Recomenda que investidores tratem criptomoedas como ativos de alto risco. --- ## A CVM e as Restrições a Fundos de Investimento em Bitcoin A **CVM** tem sido mais restritiva que o Bacen em relação a produtos financeiros baseados em criptomoedas. ### **Deliberação CVM nº 175/2022** - Proíbe fundos de investimento no exterior (FIE) de alocarem mais de **10% do patrimônio** em criptomoedas. - Impede que fundos multimercados brasileiros tenham exposição direta a Bitcoin e outras criptomoedas. ### **Instrução CVM nº 555/2021** - Estabelece que **ETFs de Bitcoin** não podem ser comercializados no Brasil sem aprovação expressa da CVM. - Até hoje, nenhum ETF de criptomoeda foi aprovado no país. --- ## **Tributação e Controles da Receita Federal** Além das restrições do Bacen e da CVM, a **Receita Federal** impõe regras rígidas para transações em Bitcoin: ### **Instrução Normativa RFB nº 1.888/2019** - Obriga declaração de todas as operações em criptomoedas acima de **R$ 35 mil** por mês. - Tributa ganhos de capital em criptomoedas em **15% a 22,5%**, dependendo do valor. --- ## **O Bitcoin Sob Vigilância do SFN** O Sistema Financeiro Nacional tem adotado medidas para **limitar a adoção em massa do Bitcoin**, seja por meio de regulamentações rígidas, restrições a fundos ou alertas sobre riscos. Enquanto o mercado de criptomoedas cresce globalmente, no Brasil ainda há um **cenário de cautela e controle**, com o SFN buscando evitar que criptomoedas desafiem a hegemonia do sistema financeiro tradicional.
@ f3873798:24b3f2f3
2025-04-02 13:50:17O Bitcoin e as criptomoedas surgiram como uma alternativa descentralizada ao sistema financeiro tradicional. No entanto, no Brasil, o **Sistema Financeiro Nacional (SFN)** tem adotado medidas para controlar e limitar a exposição de investidores e instituições a esses ativos. Neste artigo, exploraremos as principais resoluções e regulamentações que restringem o investimento em Bitcoin no país. ## **O Posicionamento do Banco Central do Brasil (Bacen)**  O Banco Central do Brasil (Bacen) e outros órgãos reguladores, como a **Comissão de Valores Mobiliários (CVM)**, têm adotado uma postura cautelosa em relação às criptomoedas. ### **Resolução Bacen nº 4.753/2021** - Proíbe que instituições financeiras ofereçam serviços de criptomoedas em suas carteiras sem autorização prévia. - Restringe bancos e corretoras de operarem diretamente com criptoativos, limitando sua integração ao sistema financeiro tradicional. ### **Comunicado do Bacen sobre Riscos das Criptomoedas** - O Bacen já emitiu alertas sobre os riscos de volatilidade, fraudes e falta de garantias em investimentos em Bitcoin. - Recomenda que investidores tratem criptomoedas como ativos de alto risco. --- ## A CVM e as Restrições a Fundos de Investimento em Bitcoin A **CVM** tem sido mais restritiva que o Bacen em relação a produtos financeiros baseados em criptomoedas. ### **Deliberação CVM nº 175/2022** - Proíbe fundos de investimento no exterior (FIE) de alocarem mais de **10% do patrimônio** em criptomoedas. - Impede que fundos multimercados brasileiros tenham exposição direta a Bitcoin e outras criptomoedas. ### **Instrução CVM nº 555/2021** - Estabelece que **ETFs de Bitcoin** não podem ser comercializados no Brasil sem aprovação expressa da CVM. - Até hoje, nenhum ETF de criptomoeda foi aprovado no país. --- ## **Tributação e Controles da Receita Federal** Além das restrições do Bacen e da CVM, a **Receita Federal** impõe regras rígidas para transações em Bitcoin: ### **Instrução Normativa RFB nº 1.888/2019** - Obriga declaração de todas as operações em criptomoedas acima de **R$ 35 mil** por mês. - Tributa ganhos de capital em criptomoedas em **15% a 22,5%**, dependendo do valor. --- ## **O Bitcoin Sob Vigilância do SFN** O Sistema Financeiro Nacional tem adotado medidas para **limitar a adoção em massa do Bitcoin**, seja por meio de regulamentações rígidas, restrições a fundos ou alertas sobre riscos. Enquanto o mercado de criptomoedas cresce globalmente, no Brasil ainda há um **cenário de cautela e controle**, com o SFN buscando evitar que criptomoedas desafiem a hegemonia do sistema financeiro tradicional. @ 06639a38:655f8f71
2025-04-02 13:47:57You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github. Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits. Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19) ### **TLV's** Things were getting more complicated with the other prefixes / identifiers defined in NIP-19: * `nevent` * `naddr` * `nprofile` This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's. _When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._ _For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._ These possible standardized `TLV` types are: * `0`_:_ `special` * _depends on the bech32 prefix:_ * _for_ `nprofile` _it will be the 32 bytes of the profile public key_ * _for_ `nevent` _it will be the 32 bytes of the event id_ * _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._ * `1`_:_ `relay` * _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_ * _this may be included multiple times_ * `2`_:_ `author` * _for_ `naddr`_, the 32 bytes of the pubkey of the event_ * _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_ * `3`_:_ `kind` * _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_ * _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_ These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters. Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code): * [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74) * [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19) ### **So what's next?** * NIP-19 code housekeeping + refactoring * Prepare a new release with NIP-19 integration * Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev)
@ 06639a38:655f8f71
2025-04-02 13:47:57You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github. Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits. Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19) ### **TLV's** Things were getting more complicated with the other prefixes / identifiers defined in NIP-19: * `nevent` * `naddr` * `nprofile` This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's. _When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._ _For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._ These possible standardized `TLV` types are: * `0`_:_ `special` * _depends on the bech32 prefix:_ * _for_ `nprofile` _it will be the 32 bytes of the profile public key_ * _for_ `nevent` _it will be the 32 bytes of the event id_ * _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._ * `1`_:_ `relay` * _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_ * _this may be included multiple times_ * `2`_:_ `author` * _for_ `naddr`_, the 32 bytes of the pubkey of the event_ * _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_ * `3`_:_ `kind` * _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_ * _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_ These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters. Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code): * [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74) * [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19) ### **So what's next?** * NIP-19 code housekeeping + refactoring * Prepare a new release with NIP-19 integration * Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev) @ 5d4b6c8d:8a1c1ee3
2025-04-02 13:15:30I've always loved Westbrook. He plays so hard and does things through sheer force of will that no one else has ever been able to do. He's also the last guy you want on the court at the end of close games. No one has ever so reliably made poor choices in late game, or even just end of clock, situations. Here are some highlights from the epic Nuggets vs T-Wolves game, which Russ completely blew at the end. https://youtu.be/rgtzQxRpH6c I've said before that I think Russ' career +/- would be 4 points higher if coaches had never let him play at the ends of quarters. Translation for non-analytics nerds: Russ has blown virtually every final possession throughout his entire career. It's unbelievable. Is there anyone I'm overlooking as a worse clutch performer? originally posted at https://stacker.news/items/932077
@ 5d4b6c8d:8a1c1ee3
2025-04-02 13:15:30I've always loved Westbrook. He plays so hard and does things through sheer force of will that no one else has ever been able to do. He's also the last guy you want on the court at the end of close games. No one has ever so reliably made poor choices in late game, or even just end of clock, situations. Here are some highlights from the epic Nuggets vs T-Wolves game, which Russ completely blew at the end. https://youtu.be/rgtzQxRpH6c I've said before that I think Russ' career +/- would be 4 points higher if coaches had never let him play at the ends of quarters. Translation for non-analytics nerds: Russ has blown virtually every final possession throughout his entire career. It's unbelievable. Is there anyone I'm overlooking as a worse clutch performer? originally posted at https://stacker.news/items/932077 @ fd06f542:8d6d54cd
2025-04-02 12:45:44## 国内开发者作品展 ### jumble.social 作品: https://jumble.social/ 其他作品 : Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️ Building 👨💻: https://github.com/CodyTseng/jumble https://github.com/CodyTseng/nostr-relay-tray https://github.com/CodyTseng/danmakustr https://github.com/CodyTseng/nostr-relay-nestjs https://github.com/CodyTseng/nostr-relay https://github.com/CodyTseng ### nostrbook.com 作品: https://nostrbook.com - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 https://www.duozhutuan.com nostrhttp demo https://github.com/duozhutuan/NostrBridge ### nostrmo A nostr dev. #Nostrmo A client support all platform. #Nowser A nostr signing project. #CacheRelay A nostr cache relay peject. #cfrelay A nostr relay base on cloudflare wokers. A nostr note timing send service. https://sendbox.nostrmo.com/ https://github.com/haorendashu/nostrmo ### nostrudel avaScript developer working on some nostr stuff - noStrudel https://nostrudel.ninja/ - Blossom https://github.com/hzrd149/blossom - Applesauce https://hzrd149.github.io/applesauce/ https://hzrd149.com/ ### nostrudel A nostr web client focused on exploring the nostr protocol https://geyser.fund/project/nostrudel
@ fd06f542:8d6d54cd
2025-04-02 12:45:44## 国内开发者作品展 ### jumble.social 作品: https://jumble.social/ 其他作品 : Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️ Building 👨💻: https://github.com/CodyTseng/jumble https://github.com/CodyTseng/nostr-relay-tray https://github.com/CodyTseng/danmakustr https://github.com/CodyTseng/nostr-relay-nestjs https://github.com/CodyTseng/nostr-relay https://github.com/CodyTseng ### nostrbook.com 作品: https://nostrbook.com - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 https://www.duozhutuan.com nostrhttp demo https://github.com/duozhutuan/NostrBridge ### nostrmo A nostr dev. #Nostrmo A client support all platform. #Nowser A nostr signing project. #CacheRelay A nostr cache relay peject. #cfrelay A nostr relay base on cloudflare wokers. A nostr note timing send service. https://sendbox.nostrmo.com/ https://github.com/haorendashu/nostrmo ### nostrudel avaScript developer working on some nostr stuff - noStrudel https://nostrudel.ninja/ - Blossom https://github.com/hzrd149/blossom - Applesauce https://hzrd149.github.io/applesauce/ https://hzrd149.com/ ### nostrudel A nostr web client focused on exploring the nostr protocol https://geyser.fund/project/nostrudel @ 7bdef7be:784a5805
2025-04-02 12:37:35The following script try, using [nak](https://github.com/fiatjaf/nak), to find out the last ten people who have followed a `target_pubkey`, sorted by the most recent. It's possibile to shorten `search_timerange` to speed up the search. ``` #!/usr/bin/env fish # Target pubkey we're looking for in the tags set target_pubkey "6e468422dfb74a5738702a8823b9b28168abab8655faacb6853cd0ee15deee93" set current_time (date +%s) set search_timerange (math $current_time - 600) # 24 hours = 86400 seconds set pubkeys (nak req --kind 3 -s $search_timerange wss://relay.damus.io/ wss://nos.lol/ 2>/dev/null | \ jq -r --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[] | select(.[0] == "p" and .[1] == $target)) | .pubkey ' | sort -u) if test -z "$pubkeys" exit 1 end set all_events "" set extended_search_timerange (math $current_time - 31536000) # One year for pubkey in $pubkeys echo "Checking $pubkey" set events (nak req --author $pubkey -l 5 -k 3 -s $extended_search_timerange wss://relay.damus.io wss://nos.lol 2>/dev/null | \ jq -c --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[][] == $target) ' 2>/dev/null) set count (echo "$events" | jq -s 'length') if test "$count" -eq 1 set all_events $all_events $events end end if test -n "$all_events" echo -e "Last people following $target_pubkey:" echo -e "" set sorted_events (printf "%s\n" $all_events | jq -r -s ' unique_by(.id) | sort_by(-.created_at) | .[] | @json ') for event in $sorted_events set npub (echo $event | jq -r '.pubkey' | nak encode npub) set created_at (echo $event | jq -r '.created_at') if test (uname) = "Darwin" set follow_date (date -r "$created_at" "+%Y-%m-%d %H:%M") else set follow_date (date -d @"$created_at" "+%Y-%m-%d %H:%M") end echo "$follow_date - $npub" end end ```
@ 7bdef7be:784a5805
2025-04-02 12:37:35The following script try, using [nak](https://github.com/fiatjaf/nak), to find out the last ten people who have followed a `target_pubkey`, sorted by the most recent. It's possibile to shorten `search_timerange` to speed up the search. ``` #!/usr/bin/env fish # Target pubkey we're looking for in the tags set target_pubkey "6e468422dfb74a5738702a8823b9b28168abab8655faacb6853cd0ee15deee93" set current_time (date +%s) set search_timerange (math $current_time - 600) # 24 hours = 86400 seconds set pubkeys (nak req --kind 3 -s $search_timerange wss://relay.damus.io/ wss://nos.lol/ 2>/dev/null | \ jq -r --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[] | select(.[0] == "p" and .[1] == $target)) | .pubkey ' | sort -u) if test -z "$pubkeys" exit 1 end set all_events "" set extended_search_timerange (math $current_time - 31536000) # One year for pubkey in $pubkeys echo "Checking $pubkey" set events (nak req --author $pubkey -l 5 -k 3 -s $extended_search_timerange wss://relay.damus.io wss://nos.lol 2>/dev/null | \ jq -c --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[][] == $target) ' 2>/dev/null) set count (echo "$events" | jq -s 'length') if test "$count" -eq 1 set all_events $all_events $events end end if test -n "$all_events" echo -e "Last people following $target_pubkey:" echo -e "" set sorted_events (printf "%s\n" $all_events | jq -r -s ' unique_by(.id) | sort_by(-.created_at) | .[] | @json ') for event in $sorted_events set npub (echo $event | jq -r '.pubkey' | nak encode npub) set created_at (echo $event | jq -r '.created_at') if test (uname) = "Darwin" set follow_date (date -r "$created_at" "+%Y-%m-%d %H:%M") else set follow_date (date -d @"$created_at" "+%Y-%m-%d %H:%M") end echo "$follow_date - $npub" end end ``` @ fd06f542:8d6d54cd
2025-04-02 12:34:07- [首页](/readme.md) - [国内开发者](/01.md)
@ fd06f542:8d6d54cd
2025-04-02 12:34:07- [首页](/readme.md) - [国内开发者](/01.md) @ 7bdef7be:784a5805
2025-04-02 12:12:12We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so **everyone can actually snoop what we are interested in**, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: **encrypted lists**. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, **we can hide the lists' content from others**. The implications are obvious: we can not only have a more organized way to browse content, but it is also **really private one**. One might wonder what use can really be made of private lists; here are some examples: * Browse “can't miss” content from users I consider a priority; * Supervise competitors or adversarial parts; * Monitor sensible topics (tags); * Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of **how many bots scan our actions to profile us**. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an **easier option** to start offering private lists: give the user **the possibility to simply mark them as local-only**, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage **both encrypted and local-only lists**. Beg your Nostr client to implement private lists!
@ 7bdef7be:784a5805
2025-04-02 12:12:12We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so **everyone can actually snoop what we are interested in**, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: **encrypted lists**. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, **we can hide the lists' content from others**. The implications are obvious: we can not only have a more organized way to browse content, but it is also **really private one**. One might wonder what use can really be made of private lists; here are some examples: * Browse “can't miss” content from users I consider a priority; * Supervise competitors or adversarial parts; * Monitor sensible topics (tags); * Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of **how many bots scan our actions to profile us**. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an **easier option** to start offering private lists: give the user **the possibility to simply mark them as local-only**, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage **both encrypted and local-only lists**. Beg your Nostr client to implement private lists! @ 7bdef7be:784a5805
2025-04-02 12:02:45We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, \*\*so everyone can actually snoop\*\* what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see \[NIP-51\](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create \*\*dedicated feeds\*\*, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be \*\*encrypted\*\*, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also \*\*really private one\*\*. One might wonder what use can really be made of private lists; here are some examples: - Browse “can't miss” content from users I consider a priority; - Supervise competitors or adversarial parts; - Monitor sensible topics (tags); - Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of \*\*how many bots scan our actions to profile us\*\*. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff (\[NIP-44\](https://github.com/nostr-protocol/nips/blob/master/51.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply \*\*mark them as local-only\*\*, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is Gossip, which permits to manage \*\*both encrypted and local-only lists\*\*. Beg your Nostr client to implement private lists!
@ 7bdef7be:784a5805
2025-04-02 12:02:45We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, \*\*so everyone can actually snoop\*\* what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see \[NIP-51\](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create \*\*dedicated feeds\*\*, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be \*\*encrypted\*\*, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also \*\*really private one\*\*. One might wonder what use can really be made of private lists; here are some examples: - Browse “can't miss” content from users I consider a priority; - Supervise competitors or adversarial parts; - Monitor sensible topics (tags); - Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of \*\*how many bots scan our actions to profile us\*\*. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff (\[NIP-44\](https://github.com/nostr-protocol/nips/blob/master/51.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply \*\*mark them as local-only\*\*, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is Gossip, which permits to manage \*\*both encrypted and local-only lists\*\*. Beg your Nostr client to implement private lists! @ 8dac122d:0fc98d37
2025-04-02 10:46:20 When selling goods or services, you might want to consider using an auction format to maximize your profits and customer satisfaction. For those of us that don't know, selling through auction is the way where the price of the item is determined by the bids of the buyers, rather than by the seller. It's an interesting approach when trying to attract more buyers and generate more exposure. It can generate a buzz around your item and business, drawing attention from potential buyers who might not otherwise be interested, with any healthier word-of-mouth marketing and social media sharing. Lately I've been reserching on this topic, thinking on how it could be implemented here on SN. Exploring other forums with more and fewer functionalities, have noticed that some really dive in with years of experience, trust build systems and the ability to offer this service with honesty and confidence. It's curious to see how all this started back in Babylon around 500 B.C., with brides as earliest known auctions “items” sold to grooms through descending bids. I'll leave you to research and discover _why_. Hopefully, ~AGORA auctions will be less problematic! # How do we reach Online Auctions perfection Firstly, I want to give you some history about “remote” auctions and how they have been evolving together with technological innovations. When TV and telephones were widely adopted in the west early in the late 80s, Nigel Myers, Director for Cox Automotive, describes the shifting mindset towards technology as: _“a time when people were really beginning to grasp what technology could do and that traditional ways of working were going to be challenged. We adopted the view that we must embrace these emerging technologies before our competitors. We considered it essential to remain at the forefront of the industry._”  AuctionVision in 1991 was the industry’s first successful intent into _“virtual auctions”_, it offered the ability to buy and sell vehicles remotely for the very first time via satellite television. It revolutionized the industry that had remained largely the same for decades and provided the foundations for what we know as online auctions today. Anyone familiar with the telethon events that were popular in the 80s and 90s can picture the scene[^1]. These auctions eventually moved and take more and more place through text-based groups and discussion lists. Yes, those times when cool UIs were not a thing, and one had to connect through the telephone line. Despite the technological challenges, such trades witnessed a huge popularity in those days and seeing the flourishing success of online trading, entrepreneurs began to realize the tremendous potential of online auctions. They understood the global reach online auction markets could have. <sub>Ebay's AuctionWeb.com website launch in 1996</sub>  It was in 1995 that the first simple online auction website was made available by Pierre Omidyar, In September 1997, the portal was officially renamed from AuctionWeb.com to eBay.com.[^2] Being the first such venture in the market, eBay had many advantages, which they utilized fully quickly becaming the biggest player in this industry. They have maintained their reputation till today, however, various websites soon came up and emerged as strong competitors to eBay. The leading competitors were Yahoo! Auctions and Amazon.com. Today we see an explosion of auction' website that cover specific markets, from cars to RE, art, clothes, snickers, Pokémon's cards , NFTs and who know how many more. # The various Auctions Formats Together with technological evolution, auctions have been adapting and evolving to market request satisfying specific needs. Let's break down the various types of auctions formats to evaluate which one could be better suited for the AGORA marketplace. #### English Auction Running with ascending bids, this is the most known and adopted worldwide. An initial value is usually defined by the auctioneer as a starting bid, meaning no less than that amount will be accepted. Bidders openly compete by raising the price with bids until the highest bid wins. It's one of the oldest formats, dating back to ancient Rome (literally called _auctus_), where soldiers auctioned war loot. Modern English auctions quickly evolved in 17th-century England for antiques and art: the Mona Lisa was almost sold in 1959 but was withdrawn when bidding stalled at $5 million (a fraction of its value today). I see this as a perfect match for our case, as it's the easiest to run manually, bids could be simply public comments for the auctioneer to easily track progress and evaluate the winner. It could be left open until no one else set more bids, or ending on a defied time set as deadline. #### Dutch Auction It is not a case, it runs with descending bids. Named as Dutch auction because it was firstly adopted in 17th-cetury's Holland to sell big quantities of perishable items like tulip bulbs (yes, that tulip mania), that if not sold quickly would end up being unsellable. The auctioneer, in this case, sets an intentionally high initial price, bids value were publicly dropped until a buyer screamed _“Mij!”_ (_Mine!_ in English) to confirm interest and stop the auctioneer lowering the price more to have more bidders interested. Today, tech helps with that: digital clocks sync with global logistics. Flowers bought by 10 AM are shipped by noon and sold in NYC by the next day. The Aalsmeer complex is 1.6 million m² (≈200 soccer fields)[^3]. Forklifts zip through 100+ km of corridors, selling over 12 billion flowers a year. Nearly 80% of global flowers, with some lots dropping from €10 to €0.50 in minutes when bidders sense oversupply. They are also called _Clock Auction_, as the price drops by the second. Bidders just need to simply press a button and get the item. <sub>Auction board from the Aalsmeer in Holland</sub>  This would be a bit harder to run here, as it would be the auctioneer making lower and lower offers in the in comments. Bidders stay unnotably silent until interested. But the Auctioner couls also be the only spectator... Fun Fact: Google’s 2004 IPO tried a Dutch auction to “democratize” share pricing, it was probably more a sealed-bid auction, but anyway, some say it wasn't a success. #### Sealed-Bid Auction First higher price win: due to this nature, it's probably obvious, it was popularized by governments, specifically for procurement contracts. For example, the U.S. Treasury Inc. has used it since the 1800s to sell bonds to bidders that privately submit offers. The auctioneer reserve the right to close receiving offers at a certain time, or when enough offers have been received to be able to select the highest(s) or the most interesting one(s). As you can understand, bidders often suffer the _winner’s curse_, most of the time ending up overpaying due to the secrecy detail. We cannot sto auctionees from posting these, but from a bidder or buyer perspective, I'd advise avoiding the participation on this format on SN. It is much riskier for the bidder and definitely doesn't much our value of transparency. Just mentioning as it is part of my research. #### Vickrey Auction (Second-Price Sealed Bid) Similar to the Sealed-bid auction, with the only difference that the winner pays the second-highest bid, for example, if you bid 0.05 BTC, and next highest is 0.04 BTC, you win the auction, but you pay 0.04 BTC. This approach, born as improvement of the previous one, incentivize to bid the true max value without penalty for honesty. Named after William Vickrey, a Nobel-winning economist who designed it in 1961 to incentivize a more truthful bidding format. A practical example are the Government (again) Spectrum Sales, where FCC uses Vickrey-inspired formats to allocate radio frequencies more fairly and try to avoid bid inflation. Good fit for stackers? Definitely not! #### Other Formats & Variations Along the centuries, auctions have evolved. Those mentioned above are the most common and adopted. Other really specific formats have been designed to fit specific markets or occasions. For example, **Silent Auctions** are an English Auction's variation, with the only difference that bids are anonymously offered in writing. Mostly used for fundraising and Ads placements, where the bidders prefer to keep certain levels of privacy. **Penny (or Incremental) Auction** is one where participants pay (historically was just 1 penny to join in, from here the name of the format) to place bids. The timer resets with each bid. Highly risky when applied to online auctions because bidders need to pay for participating. I'll avoid mentioning controversies and scams in history related to this format. Just note down that, to participate, you must really know and have full trust in the auctioneer or the people selling the items. **Reserve Auction** is where the seller or auctioneer sets a hidden minimum price; if unmet, the item will remain unsold. This could fit here: an auctioneer maybe just need to clearly state “Reserve Met” or “Reserve NOT met” publicly to close the auction, without the need to publicly disclose it in the initial post. Here a simpler table comparison with evaluation criteria for possible SN'~AGORA implementation | <sub>Format</sub> | <sub>Transparency</sub> | <sub>Trust Needed</sub> | <sub>Complexity</sub> | <sub>Fraud Risk</sub> | <sub>SN Feasibility</sub> | <sub>Best For</sub> | |------------------------|------------------|-------------------|----------------|----------------|--------------------|---------------------------------| | <sub>English</sub> | <sub>High</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>Moderate</sub> | <sub>✅ High</sub> | <sub>Common goods</sub> | | <sub>No-Reserve</sub> | <sub>High</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>High*</sub> | <sub>✅ High</sub> | <sub>Quick sales, liquidations</sub> | | <sub>Reserve</sub> | <sub>High</sub> | <sub>Medium†</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>✅ High</sub> | <sub>High-value/rare items</sub> | | <sub>Dutch</sub> | <sub>Medium</sub> | <sub>High‡</sub> | <sub>High</sub> | <sub>Moderate</sub> | <sub>⚠️ Medium</sub> | <sub>Bulk items, time-sensitive sales</sub> | | <sub>Silent</sub> | <sub>Medium</sub> | <sub>Medium</sub> | <sub>Low</sub> | <sub>Moderate</sub> | <sub>✅ High</sub> | <sub>Charity, small-scale auctions</sub> | | <sub>Sealed-Bid</sub> | <sub>Low</sub> | <sub>Very High</sub> | <sub>Medium</sub> | <sub>High</sub> | <sub>❌ Low</sub> | <sub>Private sales (niche use)</sub> | | <sub>Vickrey</sub> | <sub>Low</sub> | <sub>Very High</sub> | <sub>High</sub> | <sub>High</sub> | <sub>❌ Low</sub> | <sub>Theory-driven experiments</sub> | | <sub>Penny</sub> | <sub>High</sub> | <sub>Very High</sub> | <sub>Very High</sub> | <sub>Very High</sub> | <sub>❌ Low</sub> | <sub>(Avoid – predatory by design)</sub> | ``` Notes: - *No-Reserve: High fraud risk if starting bid is too low. - †Reserve: Transparency is higher if the reserve is disclosed upfront. - ‡Dutch: Requires strict timekeeping. ``` #### Would the AGORA succeed? The challenge to run and monitor auctions on SN still unsolved, at least for me. Considering there's not yet a publicly available rating to identify users' trust within the community, nor a private messaging or escrow service, I'll try my best to find the right matches and offer few options to inspire stackers. With further research, and I'll put together a draft guide to see what you all think about it. Ideally, receive feedback and together make this happening, fostering a more free and open market incentivizing a wider bitcoin circular economy. Thanks for reading until here, hope you find it entertaining. I'll leave you with an ending fun fact: In the 1800s, cattle auctions in Dodge City in Kansas used English-style bids, with cowboys literally _shouting_ offers. Deals were sealed with a handshake and whiskey! [^1]: Manheim at 100: How virtual auctions revolutionized the industry in the 90s Written by Manheim Content Team - 19/07/2021 - https://www.manheim.co.uk/news/2021/manheim-100-how-virtual-auctions-revolutionised-the-industry-in-the-90s [^2]: From the Web Design Museum, AuctionWeb in 1996 https://www.webdesignmuseum.org/gallery/ebay-1996 [^3]: Royal FloraHolland Flower Auction https://www.visitaalsmeer.nl/en/location/royal-floraholland-flower-auction/ originally posted at https://stacker.news/items/931997
@ 8dac122d:0fc98d37
2025-04-02 10:46:20 When selling goods or services, you might want to consider using an auction format to maximize your profits and customer satisfaction. For those of us that don't know, selling through auction is the way where the price of the item is determined by the bids of the buyers, rather than by the seller. It's an interesting approach when trying to attract more buyers and generate more exposure. It can generate a buzz around your item and business, drawing attention from potential buyers who might not otherwise be interested, with any healthier word-of-mouth marketing and social media sharing. Lately I've been reserching on this topic, thinking on how it could be implemented here on SN. Exploring other forums with more and fewer functionalities, have noticed that some really dive in with years of experience, trust build systems and the ability to offer this service with honesty and confidence. It's curious to see how all this started back in Babylon around 500 B.C., with brides as earliest known auctions “items” sold to grooms through descending bids. I'll leave you to research and discover _why_. Hopefully, ~AGORA auctions will be less problematic! # How do we reach Online Auctions perfection Firstly, I want to give you some history about “remote” auctions and how they have been evolving together with technological innovations. When TV and telephones were widely adopted in the west early in the late 80s, Nigel Myers, Director for Cox Automotive, describes the shifting mindset towards technology as: _“a time when people were really beginning to grasp what technology could do and that traditional ways of working were going to be challenged. We adopted the view that we must embrace these emerging technologies before our competitors. We considered it essential to remain at the forefront of the industry._”  AuctionVision in 1991 was the industry’s first successful intent into _“virtual auctions”_, it offered the ability to buy and sell vehicles remotely for the very first time via satellite television. It revolutionized the industry that had remained largely the same for decades and provided the foundations for what we know as online auctions today. Anyone familiar with the telethon events that were popular in the 80s and 90s can picture the scene[^1]. These auctions eventually moved and take more and more place through text-based groups and discussion lists. Yes, those times when cool UIs were not a thing, and one had to connect through the telephone line. Despite the technological challenges, such trades witnessed a huge popularity in those days and seeing the flourishing success of online trading, entrepreneurs began to realize the tremendous potential of online auctions. They understood the global reach online auction markets could have. <sub>Ebay's AuctionWeb.com website launch in 1996</sub>  It was in 1995 that the first simple online auction website was made available by Pierre Omidyar, In September 1997, the portal was officially renamed from AuctionWeb.com to eBay.com.[^2] Being the first such venture in the market, eBay had many advantages, which they utilized fully quickly becaming the biggest player in this industry. They have maintained their reputation till today, however, various websites soon came up and emerged as strong competitors to eBay. The leading competitors were Yahoo! Auctions and Amazon.com. Today we see an explosion of auction' website that cover specific markets, from cars to RE, art, clothes, snickers, Pokémon's cards , NFTs and who know how many more. # The various Auctions Formats Together with technological evolution, auctions have been adapting and evolving to market request satisfying specific needs. Let's break down the various types of auctions formats to evaluate which one could be better suited for the AGORA marketplace. #### English Auction Running with ascending bids, this is the most known and adopted worldwide. An initial value is usually defined by the auctioneer as a starting bid, meaning no less than that amount will be accepted. Bidders openly compete by raising the price with bids until the highest bid wins. It's one of the oldest formats, dating back to ancient Rome (literally called _auctus_), where soldiers auctioned war loot. Modern English auctions quickly evolved in 17th-century England for antiques and art: the Mona Lisa was almost sold in 1959 but was withdrawn when bidding stalled at $5 million (a fraction of its value today). I see this as a perfect match for our case, as it's the easiest to run manually, bids could be simply public comments for the auctioneer to easily track progress and evaluate the winner. It could be left open until no one else set more bids, or ending on a defied time set as deadline. #### Dutch Auction It is not a case, it runs with descending bids. Named as Dutch auction because it was firstly adopted in 17th-cetury's Holland to sell big quantities of perishable items like tulip bulbs (yes, that tulip mania), that if not sold quickly would end up being unsellable. The auctioneer, in this case, sets an intentionally high initial price, bids value were publicly dropped until a buyer screamed _“Mij!”_ (_Mine!_ in English) to confirm interest and stop the auctioneer lowering the price more to have more bidders interested. Today, tech helps with that: digital clocks sync with global logistics. Flowers bought by 10 AM are shipped by noon and sold in NYC by the next day. The Aalsmeer complex is 1.6 million m² (≈200 soccer fields)[^3]. Forklifts zip through 100+ km of corridors, selling over 12 billion flowers a year. Nearly 80% of global flowers, with some lots dropping from €10 to €0.50 in minutes when bidders sense oversupply. They are also called _Clock Auction_, as the price drops by the second. Bidders just need to simply press a button and get the item. <sub>Auction board from the Aalsmeer in Holland</sub>  This would be a bit harder to run here, as it would be the auctioneer making lower and lower offers in the in comments. Bidders stay unnotably silent until interested. But the Auctioner couls also be the only spectator... Fun Fact: Google’s 2004 IPO tried a Dutch auction to “democratize” share pricing, it was probably more a sealed-bid auction, but anyway, some say it wasn't a success. #### Sealed-Bid Auction First higher price win: due to this nature, it's probably obvious, it was popularized by governments, specifically for procurement contracts. For example, the U.S. Treasury Inc. has used it since the 1800s to sell bonds to bidders that privately submit offers. The auctioneer reserve the right to close receiving offers at a certain time, or when enough offers have been received to be able to select the highest(s) or the most interesting one(s). As you can understand, bidders often suffer the _winner’s curse_, most of the time ending up overpaying due to the secrecy detail. We cannot sto auctionees from posting these, but from a bidder or buyer perspective, I'd advise avoiding the participation on this format on SN. It is much riskier for the bidder and definitely doesn't much our value of transparency. Just mentioning as it is part of my research. #### Vickrey Auction (Second-Price Sealed Bid) Similar to the Sealed-bid auction, with the only difference that the winner pays the second-highest bid, for example, if you bid 0.05 BTC, and next highest is 0.04 BTC, you win the auction, but you pay 0.04 BTC. This approach, born as improvement of the previous one, incentivize to bid the true max value without penalty for honesty. Named after William Vickrey, a Nobel-winning economist who designed it in 1961 to incentivize a more truthful bidding format. A practical example are the Government (again) Spectrum Sales, where FCC uses Vickrey-inspired formats to allocate radio frequencies more fairly and try to avoid bid inflation. Good fit for stackers? Definitely not! #### Other Formats & Variations Along the centuries, auctions have evolved. Those mentioned above are the most common and adopted. Other really specific formats have been designed to fit specific markets or occasions. For example, **Silent Auctions** are an English Auction's variation, with the only difference that bids are anonymously offered in writing. Mostly used for fundraising and Ads placements, where the bidders prefer to keep certain levels of privacy. **Penny (or Incremental) Auction** is one where participants pay (historically was just 1 penny to join in, from here the name of the format) to place bids. The timer resets with each bid. Highly risky when applied to online auctions because bidders need to pay for participating. I'll avoid mentioning controversies and scams in history related to this format. Just note down that, to participate, you must really know and have full trust in the auctioneer or the people selling the items. **Reserve Auction** is where the seller or auctioneer sets a hidden minimum price; if unmet, the item will remain unsold. This could fit here: an auctioneer maybe just need to clearly state “Reserve Met” or “Reserve NOT met” publicly to close the auction, without the need to publicly disclose it in the initial post. Here a simpler table comparison with evaluation criteria for possible SN'~AGORA implementation | <sub>Format</sub> | <sub>Transparency</sub> | <sub>Trust Needed</sub> | <sub>Complexity</sub> | <sub>Fraud Risk</sub> | <sub>SN Feasibility</sub> | <sub>Best For</sub> | |------------------------|------------------|-------------------|----------------|----------------|--------------------|---------------------------------| | <sub>English</sub> | <sub>High</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>Moderate</sub> | <sub>✅ High</sub> | <sub>Common goods</sub> | | <sub>No-Reserve</sub> | <sub>High</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>High*</sub> | <sub>✅ High</sub> | <sub>Quick sales, liquidations</sub> | | <sub>Reserve</sub> | <sub>High</sub> | <sub>Medium†</sub> | <sub>Low</sub> | <sub>Low</sub> | <sub>✅ High</sub> | <sub>High-value/rare items</sub> | | <sub>Dutch</sub> | <sub>Medium</sub> | <sub>High‡</sub> | <sub>High</sub> | <sub>Moderate</sub> | <sub>⚠️ Medium</sub> | <sub>Bulk items, time-sensitive sales</sub> | | <sub>Silent</sub> | <sub>Medium</sub> | <sub>Medium</sub> | <sub>Low</sub> | <sub>Moderate</sub> | <sub>✅ High</sub> | <sub>Charity, small-scale auctions</sub> | | <sub>Sealed-Bid</sub> | <sub>Low</sub> | <sub>Very High</sub> | <sub>Medium</sub> | <sub>High</sub> | <sub>❌ Low</sub> | <sub>Private sales (niche use)</sub> | | <sub>Vickrey</sub> | <sub>Low</sub> | <sub>Very High</sub> | <sub>High</sub> | <sub>High</sub> | <sub>❌ Low</sub> | <sub>Theory-driven experiments</sub> | | <sub>Penny</sub> | <sub>High</sub> | <sub>Very High</sub> | <sub>Very High</sub> | <sub>Very High</sub> | <sub>❌ Low</sub> | <sub>(Avoid – predatory by design)</sub> | ``` Notes: - *No-Reserve: High fraud risk if starting bid is too low. - †Reserve: Transparency is higher if the reserve is disclosed upfront. - ‡Dutch: Requires strict timekeeping. ``` #### Would the AGORA succeed? The challenge to run and monitor auctions on SN still unsolved, at least for me. Considering there's not yet a publicly available rating to identify users' trust within the community, nor a private messaging or escrow service, I'll try my best to find the right matches and offer few options to inspire stackers. With further research, and I'll put together a draft guide to see what you all think about it. Ideally, receive feedback and together make this happening, fostering a more free and open market incentivizing a wider bitcoin circular economy. Thanks for reading until here, hope you find it entertaining. I'll leave you with an ending fun fact: In the 1800s, cattle auctions in Dodge City in Kansas used English-style bids, with cowboys literally _shouting_ offers. Deals were sealed with a handshake and whiskey! [^1]: Manheim at 100: How virtual auctions revolutionized the industry in the 90s Written by Manheim Content Team - 19/07/2021 - https://www.manheim.co.uk/news/2021/manheim-100-how-virtual-auctions-revolutionised-the-industry-in-the-90s [^2]: From the Web Design Museum, AuctionWeb in 1996 https://www.webdesignmuseum.org/gallery/ebay-1996 [^3]: Royal FloraHolland Flower Auction https://www.visitaalsmeer.nl/en/location/royal-floraholland-flower-auction/ originally posted at https://stacker.news/items/931997 @ d04ecf33:1d62aa90
2025-04-02 09:48:16## Physical prototyping 3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes. Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations. ## Prototypers of Ideas Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop. However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car. From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase. And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc. So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better. ## Economic Impact 3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare. Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away. ## Progress LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators. If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today. If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences. Keep printing ideas and execute on them! Learn and repeat. The path to success. #llm #ai #agi #3dp #programming
@ d04ecf33:1d62aa90
2025-04-02 09:48:16## Physical prototyping 3D printers have evolved as useful tools for rapid prototyping of physical products for inspiration and demonstration purposes. Nowadays people also use them for hobbyist endeavors. They create nice little items for pure enjoyment or very simple substitution parts that can be used regardless of industrial precision and material limitations. ## Prototypers of Ideas Similarly with LLMs, you can bounce ideas off them to better understand your own thinking and also let them generate variations of ideas. They provide inspiration, summaries, and proof-of-concept boilerplates. They are rapid prototypers for and of your ideas, creating a feedback loop. However, to use LLMs successfully, people must understand that LLMs cannot and will never discover key insights. They are not creative in a human sense, just like 3D printers cannot produce a real car. From engineering to art and business ideas, people use tools for almost all phases. The key innovation of LLMs is that they offer an effective tool to iterate faster in the ideation phase. And yes, that's true of coding too. The code that LLMs generate is not production-ready, but it is a good starting point. Beware of using the prototype as the final product, as it will inevitably backfire. Use LLMs where their high-frequency but low-quality output is justified. Situations where low-quality boilerplate makes sense include experiments and other instances like code snippets, text summaries, sketches, demo videos, mockups, etc. So, take your key idea and start the conversation. Apply critical thinking to identify where the answers lack important aspects and make mistakes, but most importantly, learn how to formulate your questions better. ## Economic Impact 3D printers lower the barrier to entry in the manufacturing of physical products. LLMs, on the other hand, lower the barrier to generating useful ideas. That is to say, they lower the barrier to produce anything and everything because ideas are the basis of any product. This has a deflationary impact and, in my estimation, will further lower the need for mediocre, unimaginative people across the board. It's the bureaucrats' nightmare. Another impactful aspect of LLMs is that they are very effective learning tools, just like 3D printers. Learning in a feedback loop used to be available only by hiring a human. Now that is one prompt and a few sats away. ## Progress LLMs need "quality data" to improve, i.e., more human insight and true creativity. Therefore, they feed on open-source. Closed-source proprietary information and "intellectual property" slow their progress, but not for long. Humans, overall, yearn for innovation more than they fear censorship and punishment. It's another Pandora's box, and the effects will never be reversed. People are essentially and foremost explainers of the world, creative innovators. If you ask me, the human touch will be necessary at least until we have true AGI, and the path LLMs are on right now can never achieve that, not in a million years. I agree with David Deutsch's take on this: To produce real AGI, we must first crack serious concepts like how Meaning, Consciousness, Creativity, and Free Will work. We don't know how far we are from that, but it's not to be found along the path of what we call AI today. If you are striving to become a better version of yourself and learn every day, rest assured: LLMs are your leverage. Otherwise, you will need some fiat authority, like the state today, to force others to value your work while it has an overall negative impact (90% in that category in my estimation). People like that need a shift of perspective or will suffer the consequences. Keep printing ideas and execute on them! Learn and repeat. The path to success. #llm #ai #agi #3dp #programming @ a60e79e0:1e0e6813
2025-04-02 08:26:48*This is a long form note of a post that lives on my Nostr educational website [Hello Nostr](https://hellonostr.xyz).* So you've got yourself [started](https://hellonostr.xyz/start), you're up to speed with the latest Nostr [jargon](https://hellonostr.xyz/glossary) and you've learned the basics about the [protocol](https://hellonostr.xyz/101), but you're left wanting more!? Well, look no further! This post contains a useful list of Nostr based utilities than can enhance your experience in and around the Nostr protocol. ## Search and Discovery Getting started with Nostr can sometimes feel like a lonely journey, particularly if you're the first of your friends and family to discover how awesome it can be! These tools can help you discover new content, connect with existing follows from other networks and just generally have a poke around at the different types of content Nostr has to offer. > Have a hobby or existing community elsewhere? Have a search for it here to find others with shared interests - **[Nostr.Band](https://nostr.band/)** - Search for people, posts, media and stats literally anything Nostr has to offer! - **[Nostr.Directory](https://nostr.directory/)** - Find your Twitter follows on Nostr - **[Awesome Nostr](https://github.com/aljazceru/awesome-nostr#implementations)** - Extensive list of Relay software - **[Nostr View](https://nostrview.com/)** - Generic Nostr search 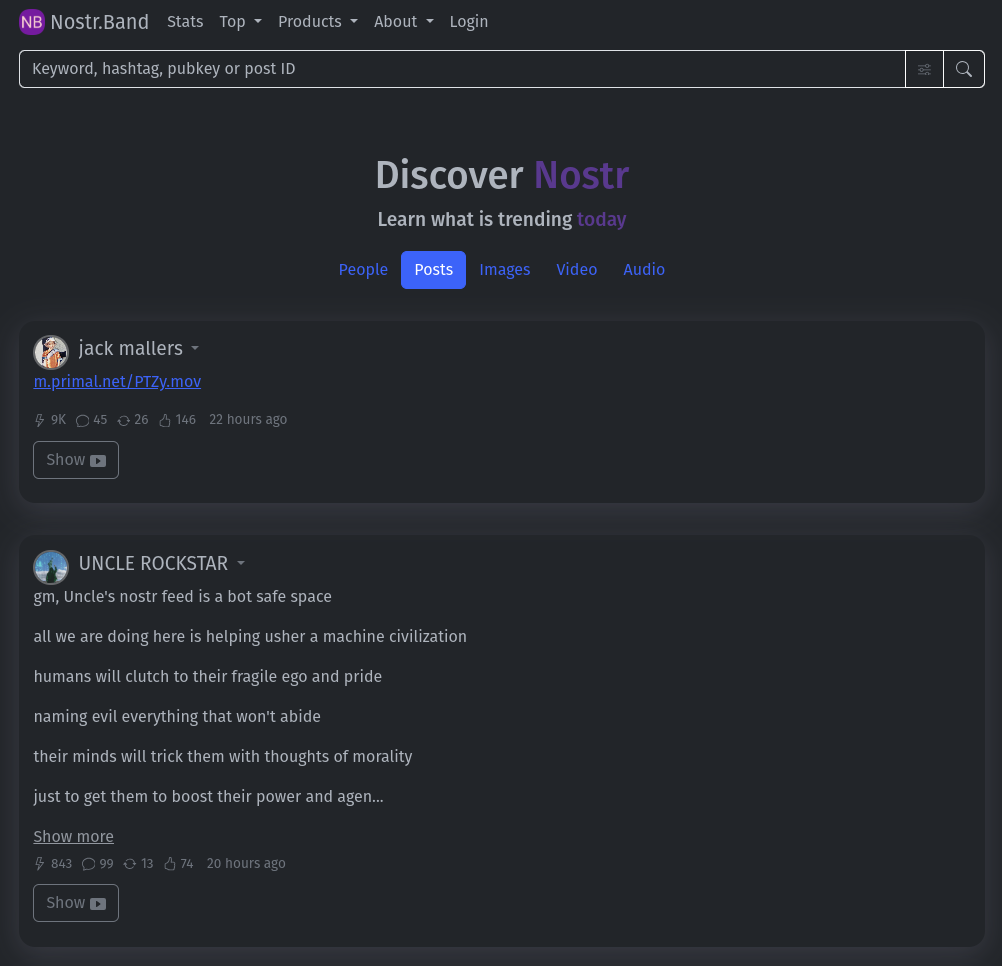 <br/> ## Relays Relays might not be the sexiest of topics, particularly for newcomers to the network, but they are a crucial part of what makes Nostr great. As you become more competent, you'll want to customize your relay selection and maybe even run your own! Here are some great starting points. > Running a personal relay is a powerful way to improve the redundancy of your Nostr events. - **[Nostr.Watch](https://next.nostr.watch/)** - Browse, test and research Nostr relays - **[Nostrwat.ch](https://nostrwat.ch/)** - List of active Nostr relays - **[Advanced Nostr Search](https://advancednostrsearch.vercel.app/)** - Targetted search with date ranges - **[Nostr.Wine](https://nostr.wine/)** - Reliable paid Relay 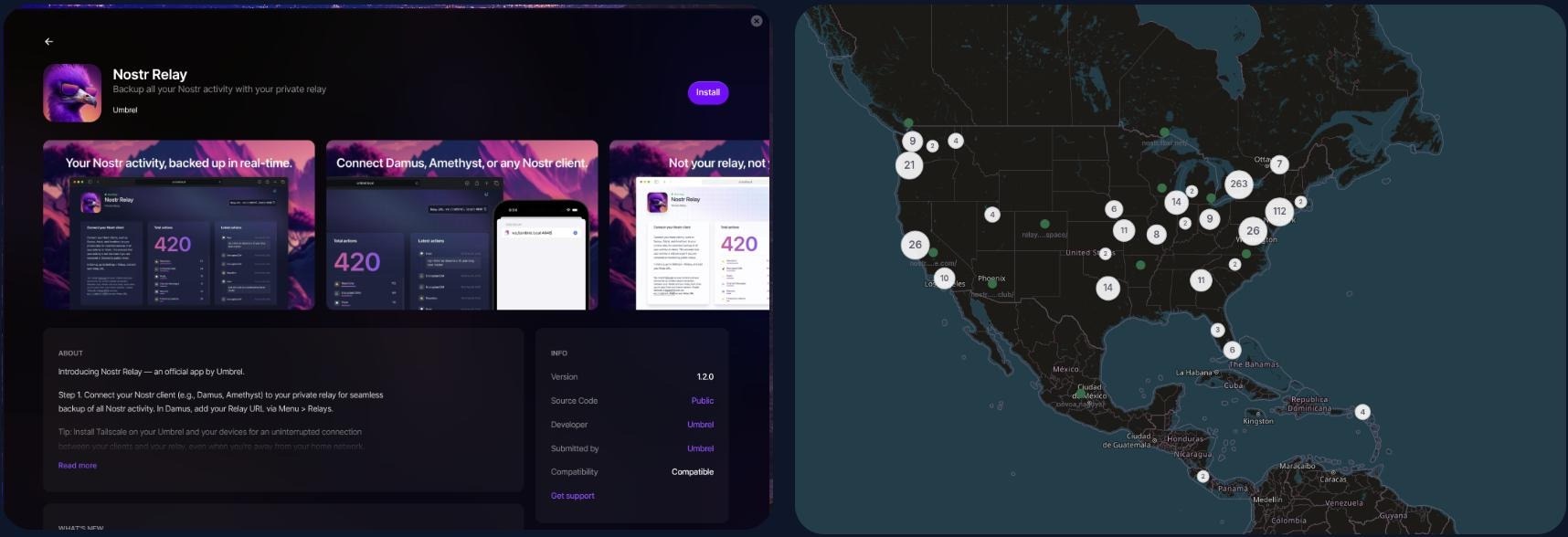 <br/> ## NIP-05 Identity Services Your nPub, or public key (that long string of letters and numbers) is your ‘official’ Nostr ID, but it’s not exactly catchy. NIP-05 identifiers are a human-readable and easily shareable way to have people find you on Nostr. They look like an email address, like qna@hellonostr.xyz. If you have your own domain and web server, you can easily [create your own](https://thebitcoinmanual.com/articles/nostr-account-nip-05-verified/) NIP-05 identifier in just a few minutes. If you don't, you'll want to leverage one of the many free or paid solutions. > Make yourself easier to find on Nostr with a NIP-05 identifier - **[Bitcoiner.Chat](https://bitcoiner.chat/)** - Free service operated by [QnA](nostr:npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx) - **[Nostr Plebs](https://nostrplebs.com/)** - Paid service with extra features - **[Alby](https://getalby.com/)** - Lightning wallet with + NIP-05 solution - **[Nostr Address](https://en.nostraddress.com/)** - Paid service with extra features - **[Zaps.Lol](https://zaps.lol/)** - Free service  <br/> ## Key Management Your private key (or nsec) it the key to your Nostr world. It is what allows you to access and interact with your social graph from any client. It doesn't matter if that client is a micro-blogging app like Amethyst, a podcast app like Fountain, or a P2P marketplace like Plebeian Market, your nsec is paramount to those interactions. Should your nsec be lost, or fall into the wrong hands, whoever then holds a copy can access Nostr and pretend to be you, meaning that you'll need to start again with a new keypair. Not a nice situation to find yourself in, so treat your nsec VERY carefully. > Your private key IS your Nostr identity. Treat it with extreme care and do not share it. - **[Alby](https://getalby.com/)** - Browser extension enabling you to sign into web app without sharing the private key - **[Nos2x](https://github.com/fiatjaf/nos2x)** - Another browser extension key manager - **[Keys.Band](https://keys.band/)** - Another browser extension key manager - **[Amber](https://github.com/greenart7c3/amber)** - Android app for safe nsec storage. Can talk to other clients on the same phone to log in and sign events - **[Nostr Signing Device](https://github.com/lnbits/nostr-signing-device)** - Dedicated device to store your nsec - **[Passport](https://docs.foundation.xyz)** - Hardware wallet for offline and deterministic nsec generation and storage 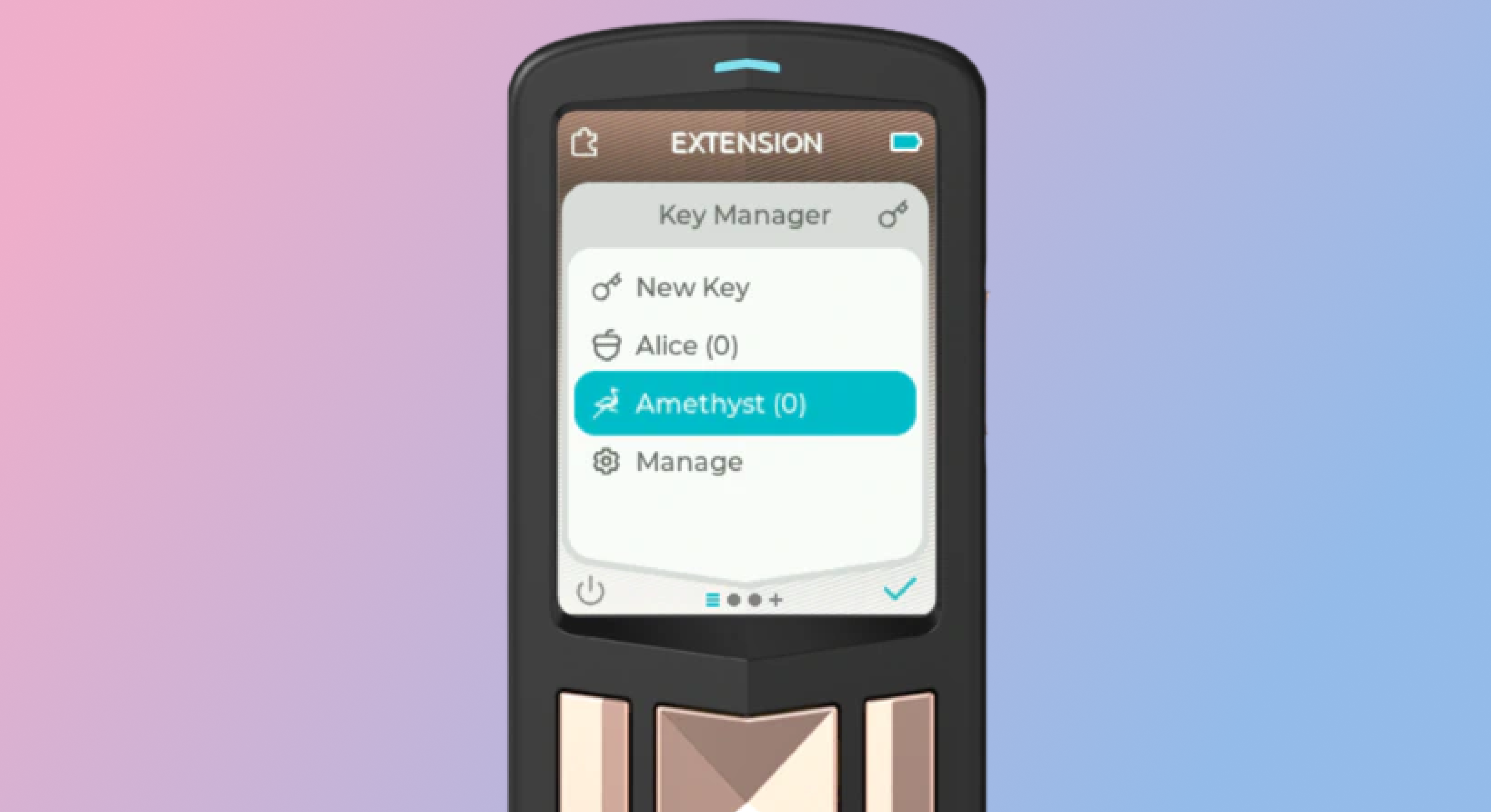 <br/> ## Zap Tools Zaps are one of the most fun parts of Nostr. Never before have we been able to send fractions of a penny, instantly to our friends because their meme made us laugh, or their blog post was very insightful. Zaps use Bitcoin’s Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider. - **[Alby](https://getalby.com/)** - Browser extension and self-custodial Lightning wallet - **[LNBits](https://github.com/lnbits/lnbits)** - A Zap server running on your own Bitcoin node - **[BTCPay Server](https://btcpayserver.org/)** - Another Zap server running on your own Bitcoin node - **[Zeus](https://github.com/ZeusLN/zeus)** - Zap compatible self-custodial mobile Lightning wallet - **[Nostr Wallet Connect](https://nwc.dev/)** - Communication protocol between Lightning wallets and Nostr apps - **[Ecash Wallets](https://github.com/cashubtc/awesome-cashu)** - Custodial Ecash based wallets that are interoperable with Lightning and Nostr (Funds may be at risk) - **[Wallet of Satoshi](https://www.walletofsatoshi.com/)** - Custodial Lightning wallet (Funds may be at risk) 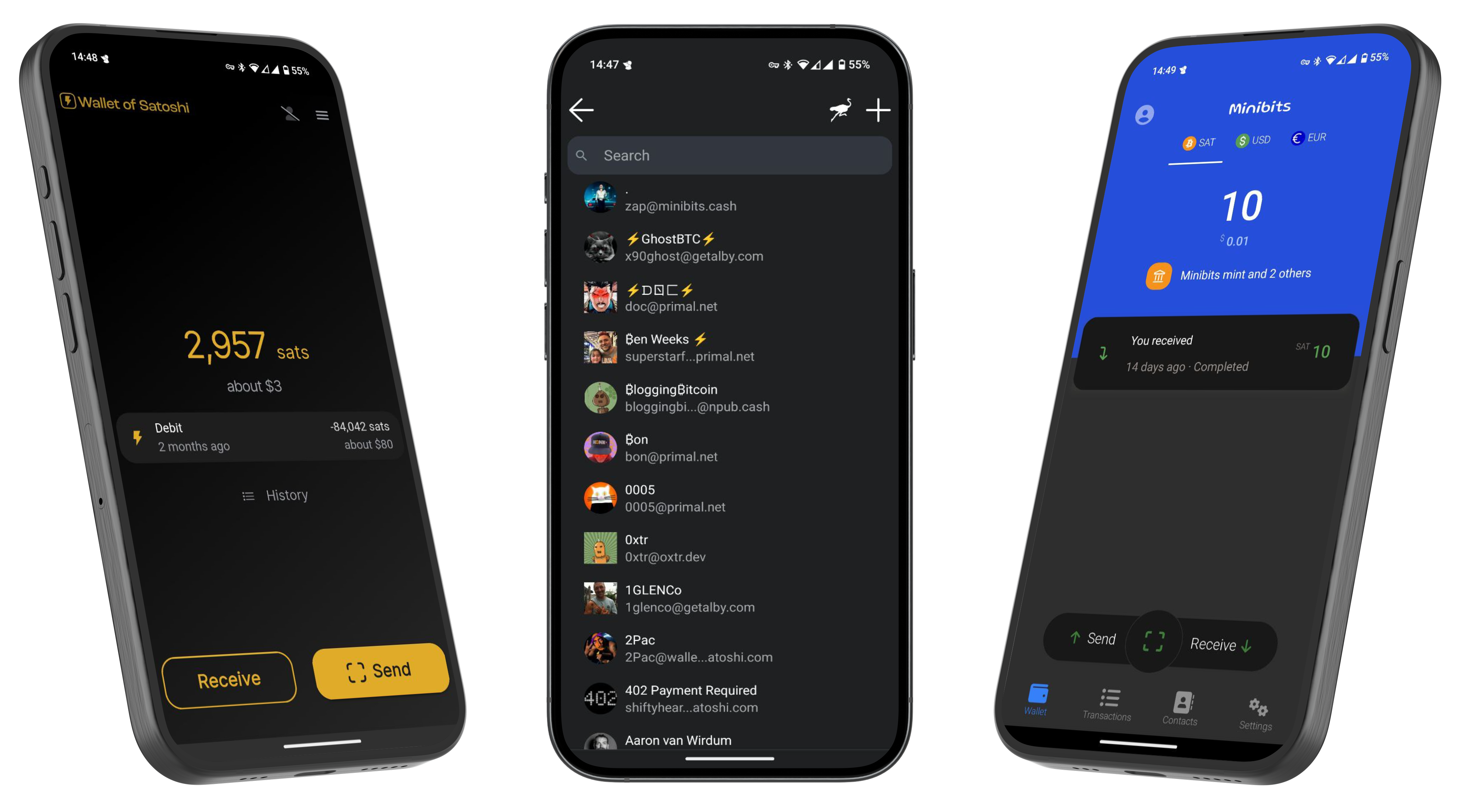 --- If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I'll be sure to Zap you back! ⚡️
@ a60e79e0:1e0e6813
2025-04-02 08:26:48*This is a long form note of a post that lives on my Nostr educational website [Hello Nostr](https://hellonostr.xyz).* So you've got yourself [started](https://hellonostr.xyz/start), you're up to speed with the latest Nostr [jargon](https://hellonostr.xyz/glossary) and you've learned the basics about the [protocol](https://hellonostr.xyz/101), but you're left wanting more!? Well, look no further! This post contains a useful list of Nostr based utilities than can enhance your experience in and around the Nostr protocol. ## Search and Discovery Getting started with Nostr can sometimes feel like a lonely journey, particularly if you're the first of your friends and family to discover how awesome it can be! These tools can help you discover new content, connect with existing follows from other networks and just generally have a poke around at the different types of content Nostr has to offer. > Have a hobby or existing community elsewhere? Have a search for it here to find others with shared interests - **[Nostr.Band](https://nostr.band/)** - Search for people, posts, media and stats literally anything Nostr has to offer! - **[Nostr.Directory](https://nostr.directory/)** - Find your Twitter follows on Nostr - **[Awesome Nostr](https://github.com/aljazceru/awesome-nostr#implementations)** - Extensive list of Relay software - **[Nostr View](https://nostrview.com/)** - Generic Nostr search  <br/> ## Relays Relays might not be the sexiest of topics, particularly for newcomers to the network, but they are a crucial part of what makes Nostr great. As you become more competent, you'll want to customize your relay selection and maybe even run your own! Here are some great starting points. > Running a personal relay is a powerful way to improve the redundancy of your Nostr events. - **[Nostr.Watch](https://next.nostr.watch/)** - Browse, test and research Nostr relays - **[Nostrwat.ch](https://nostrwat.ch/)** - List of active Nostr relays - **[Advanced Nostr Search](https://advancednostrsearch.vercel.app/)** - Targetted search with date ranges - **[Nostr.Wine](https://nostr.wine/)** - Reliable paid Relay 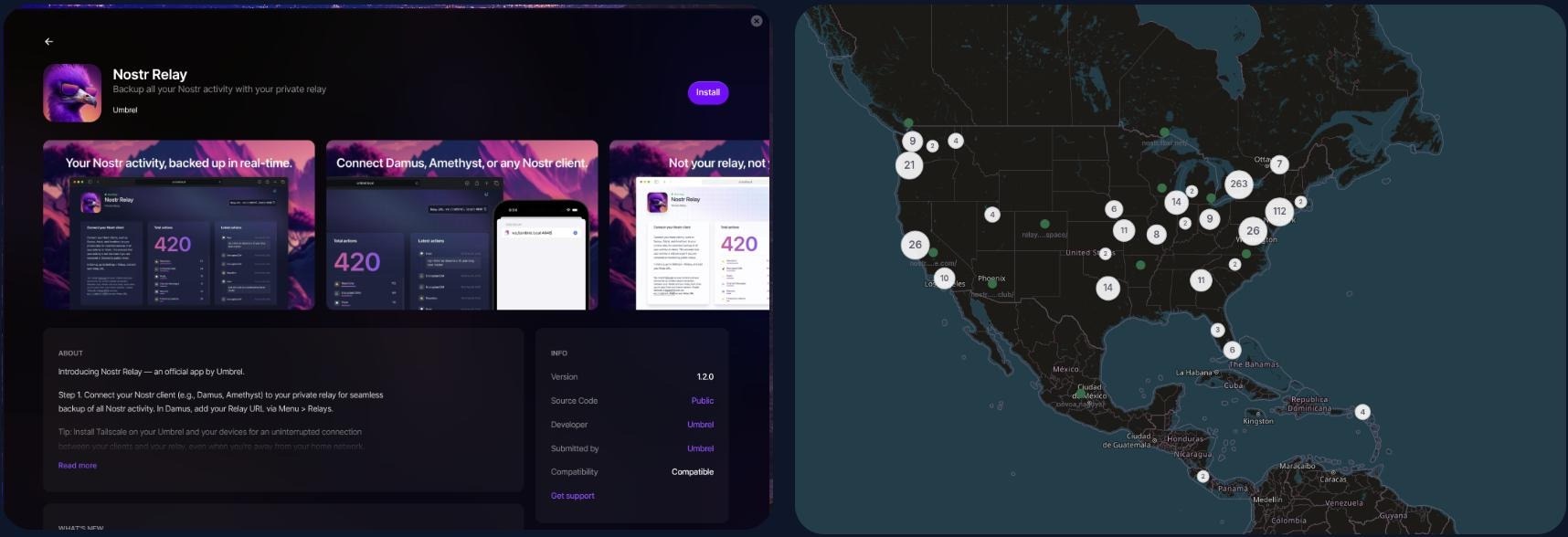 <br/> ## NIP-05 Identity Services Your nPub, or public key (that long string of letters and numbers) is your ‘official’ Nostr ID, but it’s not exactly catchy. NIP-05 identifiers are a human-readable and easily shareable way to have people find you on Nostr. They look like an email address, like qna@hellonostr.xyz. If you have your own domain and web server, you can easily [create your own](https://thebitcoinmanual.com/articles/nostr-account-nip-05-verified/) NIP-05 identifier in just a few minutes. If you don't, you'll want to leverage one of the many free or paid solutions. > Make yourself easier to find on Nostr with a NIP-05 identifier - **[Bitcoiner.Chat](https://bitcoiner.chat/)** - Free service operated by [QnA](nostr:npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx) - **[Nostr Plebs](https://nostrplebs.com/)** - Paid service with extra features - **[Alby](https://getalby.com/)** - Lightning wallet with + NIP-05 solution - **[Nostr Address](https://en.nostraddress.com/)** - Paid service with extra features - **[Zaps.Lol](https://zaps.lol/)** - Free service 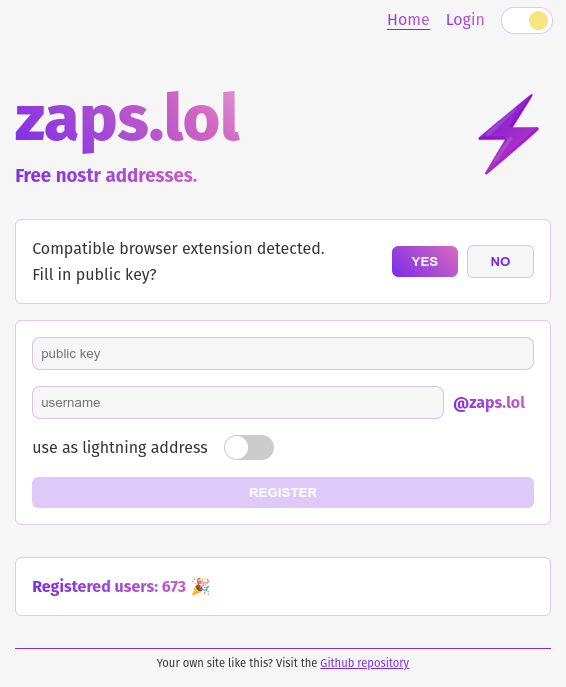 <br/> ## Key Management Your private key (or nsec) it the key to your Nostr world. It is what allows you to access and interact with your social graph from any client. It doesn't matter if that client is a micro-blogging app like Amethyst, a podcast app like Fountain, or a P2P marketplace like Plebeian Market, your nsec is paramount to those interactions. Should your nsec be lost, or fall into the wrong hands, whoever then holds a copy can access Nostr and pretend to be you, meaning that you'll need to start again with a new keypair. Not a nice situation to find yourself in, so treat your nsec VERY carefully. > Your private key IS your Nostr identity. Treat it with extreme care and do not share it. - **[Alby](https://getalby.com/)** - Browser extension enabling you to sign into web app without sharing the private key - **[Nos2x](https://github.com/fiatjaf/nos2x)** - Another browser extension key manager - **[Keys.Band](https://keys.band/)** - Another browser extension key manager - **[Amber](https://github.com/greenart7c3/amber)** - Android app for safe nsec storage. Can talk to other clients on the same phone to log in and sign events - **[Nostr Signing Device](https://github.com/lnbits/nostr-signing-device)** - Dedicated device to store your nsec - **[Passport](https://docs.foundation.xyz)** - Hardware wallet for offline and deterministic nsec generation and storage 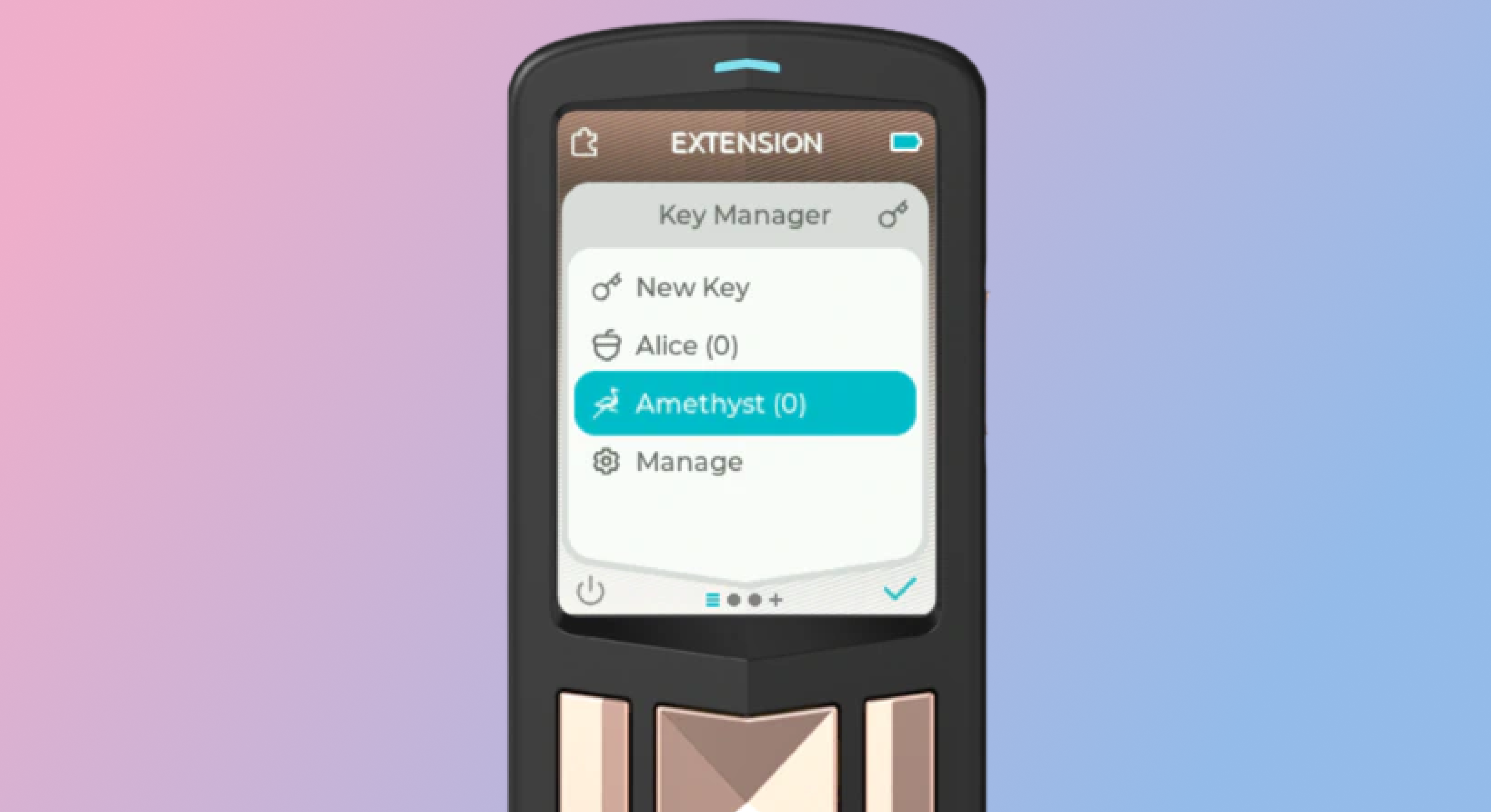 <br/> ## Zap Tools Zaps are one of the most fun parts of Nostr. Never before have we been able to send fractions of a penny, instantly to our friends because their meme made us laugh, or their blog post was very insightful. Zaps use Bitcoin’s Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider. - **[Alby](https://getalby.com/)** - Browser extension and self-custodial Lightning wallet - **[LNBits](https://github.com/lnbits/lnbits)** - A Zap server running on your own Bitcoin node - **[BTCPay Server](https://btcpayserver.org/)** - Another Zap server running on your own Bitcoin node - **[Zeus](https://github.com/ZeusLN/zeus)** - Zap compatible self-custodial mobile Lightning wallet - **[Nostr Wallet Connect](https://nwc.dev/)** - Communication protocol between Lightning wallets and Nostr apps - **[Ecash Wallets](https://github.com/cashubtc/awesome-cashu)** - Custodial Ecash based wallets that are interoperable with Lightning and Nostr (Funds may be at risk) - **[Wallet of Satoshi](https://www.walletofsatoshi.com/)** - Custodial Lightning wallet (Funds may be at risk) 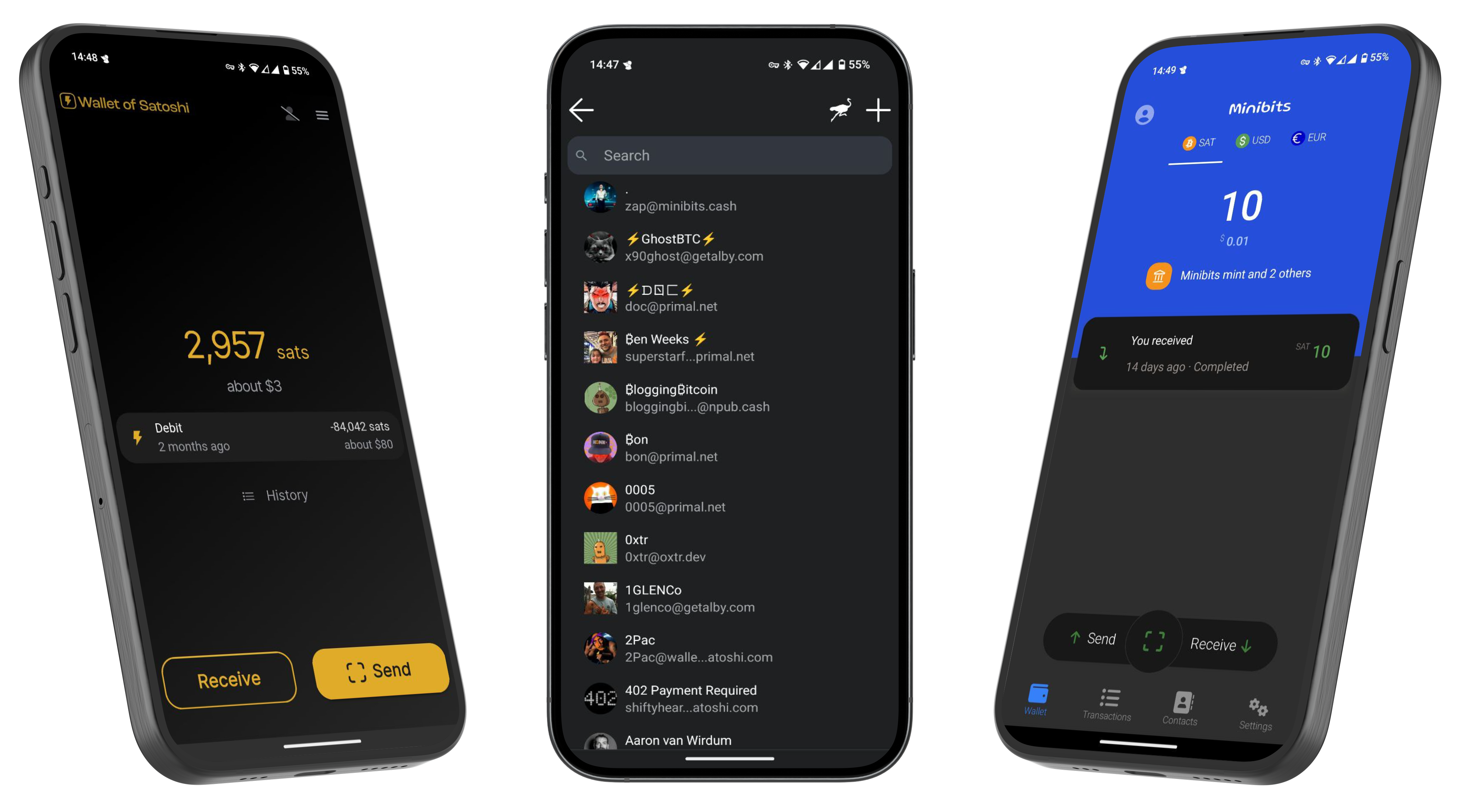 --- If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I'll be sure to Zap you back! ⚡️