-
 @ cff1720e:15c7e2b2
2025-04-11 12:00:25
@ cff1720e:15c7e2b2
2025-04-11 12:00:25Die Protagonisten\ - Puschkin, russischer Dichter (unbeteiligt, da tot)\ - Putin, russischer Präsident, Erzschurke (wahlweise Satan)\ - Tino, Musiker mit fehlender Russland-Distanz \ - Tobias, ein ebenfalls umstrittener Künstler (Querdenker) \ - Anne, Redakteurin bei einer Provinz-Zeitung (BNN) \ - DRG, Deutsch-Russische Gesellschaft Ettlingen
Ursprünglich ging es um Kunst. Die Deutsch-Russische Gesellschaft Ettlingen hatte für den Abend des 5. April zu einem Puschkin-Abend in das schöne Ettlinger Schloss eingeladen. Doch dann bekam die Presse Wind davon, und aus der geplanten Kulturveranstaltung wurde ein Politikum. Redakteurin Anne fühlte sich veranlasst den Musiker Tino einer strengen Gewissensprüfung zu unterziehen, da wachsame Bürger bzgl. seiner Person “Bedenken” geäußert haben sollen (potentieller Gemeinwohl- oder Demokratie-Gefährder?). Hier der Text ihrer Mail:\ \ Sehr geehrter Herr Eisbrenner, \ am Samstag kommen Sie für einen Auftritt nach Ettlingen. Im Vorfeld sind nun Bürger auf uns zugekommen mit Bedenken. Sie als Künstler seien „zu russlandfreundlich“.\ Gerne möchten wir natürlich auch Sie dazu zu Wort kommen lassen, um das sachlich einzuordnen.\ Ich freue mich, wenn Sie mir deswegen kurz folgende Fragen beantworten könnten:\ \ • Wie würden Sie sich selbst politisch einordnen? \ • Auf einer Veranstaltung 2023 bei der Rosa-Luxemburg-Stiftung haben Sie sich laut Medien-Berichten lobend über Putin geäußert. („Eisbrenner lobt den russischen Präsidenten Wladimir Putin, wie lange sich dieser im Konflikt mit Ukraine und Nato gezügelt habe. (…) Respekt äußert Eisbrenner auch für einen Kurswechsel unter Putin.“) Können Sie das bestätigen? Was ist heute Ihre Meinung über den russischen Präsidenten?\ • Sie haben zwei Mal am Festival „Road to Yalta“ in Moskau teilgenommen. Die Veranstalter beschreiben Sie als „Öffentlichen Fürsprecher für Russland“. Besteht die Gefahr, dass Sie von Russland instrumentalisiert werden?\ \ Um aktuell berichten zu können, brauchen wir Ihre Antworten bis morgen Mittag, 14.30 Uhr.\ Herzlichen Dank im Voraus.\ \ Mit freundlichen Grüßen \ Anne Herder\ Badische Neueste Nachrichten\ \ Angesichts der deutschen Beteiligung am Stellvertreterkrieg gegen Russland war die Wachsamkeit von Bürgern und Regionalpresse lobenswert, schließlich ging es darum den Auftritt eines “Putin-Freundes” zu verhindern. Leider hat die aufmerksame Öffentlichkeit dabei völlig übersehen dass auch Tinos musikalischer Partner Tobias ein umstrittener Künstler mit Kontakten zu “Querdenkern” ist (Wikipedia). Da der Musiker Tino in seiner Antwortmail an die Redakteurin Anne weder Bedauern noch Reue erkennen ließ, veröffentlichte sie pflichtschuldig am 4. April einen Artikel mit einer Warnung vor “russischer Propaganda”.

Trotz dieser drohenden Gefahr wollte die DRG Ettlingen sich weder vom Musiker Tino distanzieren noch die Veranstaltung absagen, mit der fragwürdigen Begründung “… die allermeisten Menschen wollen zusammen in Frieden leben."\ \ Der Puschkin-Abend fand also statt, und es sollte sogar noch schlimmer kommen, wie wir aus einer weiteren Mail von Redakteurin Anne nach der Veranstaltung erfahren können.
\ Sehr geehrter Herr Eisbrenner,\ vielen Dank für Ihre ausführliche Rückmeldung. Es freut mich zu hören, dass die Veranstaltung ein Erfolg war und der Ankündigungsartikel dazu beitragen konnte, weiteres Publikum zu gewinnen. …\ \ … Abschließend möchte ich betonen, dass es uns ein Anliegen ist, fair und ausgewogen zu berichten. Ich habe in meinem Artikel sowohl die kritischen Stimmen als auch die Positionen von Ihnen und dem Veranstalter berücksichtigt. Ziel war es, ein ausgewogenes Bild zu vermitteln und den Lesern die Möglichkeit zu geben, sich selbst eine Meinung zu bilden. \ \ Es ist nicht unsere Absicht, Personen aufgrund ihrer politischen Äußerungen oder künstlerischen Engagements zu diffamieren. Wir sind uns der Verantwortung bewusst, die wir als Medium tragen.\ \ Die tapfere Redakteurin knickte ein, beglückwünschte den “Putin-Freund” für die erfolgreiche Veranstaltung, und erklärt ihr journalistisches Verständnis damit “den Lesern die Möglichkeit zu geben, sich selbst eine Meinung zu bilden.” Keine Einordnung mehr, keine Haltung, keine kritische Distanz? Die Russland-Versteher hatten gesiegt und der Musiker Tino musste sich in seiner Antwortmail sogar bemühen nicht zu viel Nähe entstehen zu lassen: … darum möchte ich Ihnen auch nochmal und dieses Mal kurz antworten, um uns beide nicht für die Zukunft zu einer Art langjährigen „Brieffreundschaft“ zu nötigen.
Damit scheint sich Journalistin Anne nicht für höhere Aufgaben empfohlen zu haben.\ \ Resümee: Kultur kennt keine Grenzen. Deutschland ist noch nicht kriegstüchtig. Zum Glück!
Hinweis: die Inhalte der Mails sind sehr informativ, deshalb befinden sie sich in voller Länge im Anhang
Fortsetzung: eine Vertiefung des Themas gibt es im Artikel "Der Brückenbauer"
Quellen:
https://www.eisbrenner.de/ \ https://www.eisbrenner.de/programm/puschkin/ \ https://www.nachdenkseiten.de/?p=130806 \ https://bnn.de/karlsruhe/ettlingen/kritik-an-konzert-im-ettlinger-schloss-wo-steht-tino-eisbrenner-politisch \ (Artikel hinter einer Paywall)\ https://de.wikipedia.org/wiki/Tobias_Morgenstern \ https://drg-ettlingen.de/
\ Hier die Mails in voller Länge
https://route96.pareto.space/c20c13782fbd7d93b590222cb7ca7c4e1d1b485828f52e8946d36c7d2ebe376d.pdf
-
 @ cff1720e:15c7e2b2
2025-04-11 11:50:47
@ cff1720e:15c7e2b2
2025-04-11 11:50:47Zunächst einmal gilt es zu konstatieren, dass beide Optionen der Frage nicht faktisch feststellbar sind. Der Status Putin-Freund würde zumindest die Tatsache persönlicher Treffen in der Vergangenheit voraussetzen, darüber hat bisher kein Medium berichtet, also scheint es keine gegeben zu haben. Indes gibt es reichlich dokumentierte Äußerungen und Handlungen von Tino Eisbrenner die den symbolischen Begriff "Brückenbauer" rechtfertigen.
“Das zeigt mir, dass mein Glaube an Dialog, Diplomatie und (Völker)verständigung nicht unberechtigt ist.” \ (aus einer Mail an Anne Herder)
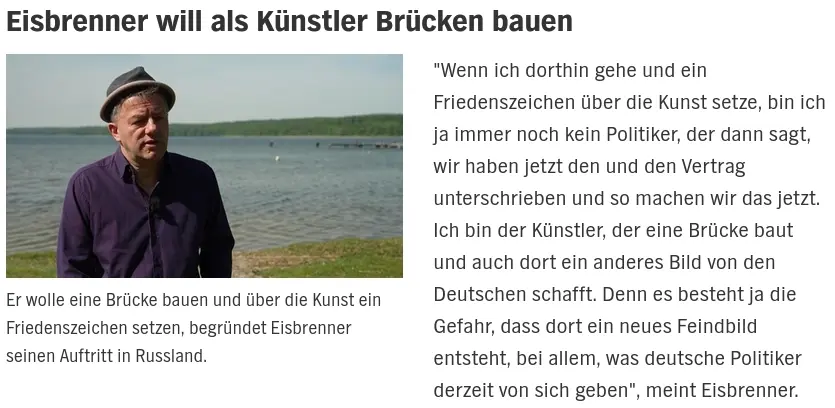
Ein zentrales Thema seiner künstlerischen Arbeit seit über einem Jahrzehnt ist die Warnung vor Völkerhass und Kriegsgefahr.
“Sie sagen ja, Sie bezögen keine Stellung. Und doch sind wir in Deutschland in eine Situation geraten, in der dieser militärische Ausdruck, Stellung beziehen, immer mehr zur Realität wird. Wir ziehen Gräben und bauen Stellungen aus, die wir dann beziehen. Durch unbedachte Überschriften, nicht eindeutige Begriffe, vermiedene Kontextualisierung und Informationen, die uns nicht gegeben werden, während wir auf Kriegstüchtigkeit eingestimmt werden und Puschkin, wenn wir nicht achtgeben, nie kennenlernen.” (aus einer Mail an Anne Herder)
„Vom Pulverfass runter!“: Tino Eisbrenner für Frieden mit Russland 5. April 2019\ https://www.textstelle.news/2019/04/05/liedermacher-tino-eisbrenner-frieden-mit-russland/
Ergänzend zu seinen Liedern und Interviews veröffentlichte Eisbrenner das Buch "Das Lied vom Frieden". https://shop.strato.de/epages/187541.sf/de_DE/?ObjectPath=/Shops/187541/Products/4657
\ Er wolle mit seinem Buch eine Diskussion anregen und dass in der Gesellschaft „noch einmal nachgedacht und diskutiert wird“. Beides ist aktuell höchst notwendig, da Politik und Medien systematisch eine gefährliche Kriegshysterie schüren, die bereits jetzt fatale Folgen für die Gesellschaft zeitigt.
"Dass einem Songschreiber, der sich für eine bessere Verständigung zwischen Westeuropa und Russland ausspricht, nicht nur Blumen auf den Weg gestreut werden, erfährt man auch aus dem vorliegendem Buch. Aber vor allem beschreibt Tino Eisbrenner seine Erlebnisse und Eindrücke auf den »Musik statt Krieg«-Tourneen, die er seit Ende 2015 durch Deutschland, Österreich und Osteuropa gemacht hat. Russland, Georgien, Belarus, Polen, Tschechien hat er viele Male mit Musik bereist und dabei interessante Menschen und deren Sicht auf das Leben, die Heimat, ihre Geschichte und auch auf Deutschland kennengelernt."
Eisbrenner belässt es nicht bei Diskussionen, er engagiert sich für vielfältige Friedens-Initiativen ungeachtet persönlicher Anfeindungen und beruflicher Nachteile. Er hat nicht nur das »Lied vom Frieden« als Song getextet, sondern lebt es auch mit dem, was er als Künstler initiiert und (re)präsentiert. Seit sechzehn Jahren veranstaltet er sein eigenes Festival »Musik statt Krieg«.

-
 @ fd06f542:8d6d54cd
2025-04-11 11:23:03
@ fd06f542:8d6d54cd
2025-04-11 11:23:03使用nostrbook.com网站
登录和创建用户:
 登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。
登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。注册:
 可以点击红标位置 生成你的账户。 “确定” 完成注册。
可以点击红标位置 生成你的账户。 “确定” 完成注册。创建书籍
封面的上传
 创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。
创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。或者点击浏览 本地图片文件。
标题和作者
正常填写就可以。 书的作者和上传文件人没有一一绑定。
写书
 创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。
创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。列出你创建的所有的书籍

点击图标,就可以进入开始写作了。例如《nostrbook站点日记》

如图所示有4个部分
- (1)关闭按钮,点击就退出编辑,这时候他会提示你保存,如果不需要保存退出,点击 “不保存退出”
- (2)
大纲是编写 你书籍的大纲,这个参考 docsify文档 下面会有例子。时间排列是 你所有为本书写的章节。但是有些章节你可能废弃了,或者暂时不想展示,都会存在 时间排列里面,就是按照你编写的时间倒序排列的。草稿是你暂时存储的内容,没有上传到网络,存在你本地浏览器的缓存里面。 - (3)这个部分看到的就是你的章节列表,当让你第一次来的这个地方是空的。
新增章节下一次就会有内容了。 - (4)文件名,是我们存储章节的唯一标识。
readme.md和_sidebar.md是系统默认必须有的。因为docsify技术默认需要这2个。
如何编写大纲
点击
更新大纲按钮- [首页](/readme.md) - [国人开发者](/01.md) - [中文用户列表](/02.md)大纲例子,“[]” 内是标题,“()”内是 文件名; 标题是是显示在文章的右侧; 文件名的作用是匹配 ‘新增章节’ 里面的markdown的相匹配关联的。
-
 @ bf95e1a4:ebdcc848
2025-04-11 11:21:48
@ bf95e1a4:ebdcc848
2025-04-11 11:21:48This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
An Immaculate Conception
Some concepts in nature are harder for us humans to understand than others. How complex things can emerge out of simpler ones is one of those concepts. A termite colony, for instance, has a complex cooling system at its lower levels. No single termite knows how it works. Completely unaware of the end results, they build complex mounds and nests, shelter tubes to protect their paths, and networks of subterranean tunnels to connect their dirt cities. Everything seems organized and designed, but it is not. Evolution has equipped the termite with a pheromone receptor that tells the termite what task he ought to engage himself in by simply counting the number of neighboring termites doing the same thing. If there’s a surplus of workers in an area, nearby termites become warriors, and so on. Complex structures emerge from simple rules. The fractal patterns found all around nature are another example. Fractals look complex, but in reality, they’re not. They’re basically algorithms — the same pattern, repeated over and over again with a slightly modified starting point. The human brain is an excellent example of a complex thing that evolved out of simpler things, and we humans still have a hard time accepting that it wasn’t designed. Religions, which themselves are emergent systems spawned out of human interaction, have come up with a plethora of explanations for how we came to be. All sorts of wild origin stories have been more widely accepted than the simple explanation that our complexities just emerged out of simpler things following a set of rules that nature itself provided our world with.
Complex systems emerge out of human interactions all the time. The phone in your pocket is the result of a century of mostly free global market competition, and no single human could ever have come up with the entire thing. The device, together with its internet connection, is capable of a lot more than the sum of its individual parts. A pocket-sized gadget that can grant instant access to almost all of the world’s literature, music, and film, which fits in your pocket, was an unthinkable science fiction a mere twenty years ago. Bitcoin, first described in Satoshi Nakamoto’s whitepaper ten years before these words were written, was designed to be decentralized. Still, it wasn’t until years later that the network started to show actual proof of this. Sound money, or absolute digital scarcity, emerged out of the network not only because of its technical design. How Bitcoin’s first ten years actually unfolded played a huge part in how true decentralization could emerge, and this is also the main reason why the experiment cannot be replicated. Scarcity on the internet could only be invented once. Satoshi’s disappearance was Bitcoin’s first step towards true decentralization. No marketing whatsoever and the randomness of who hopped onto the train first were the steps that followed. Bitcoin truly had an immaculate conception.
The network has shown a remarkable resistance to change over the last few years especially, and its current state might be its last incarnation given the size of the network and the 95% agreement threshold in its consensus rules. It might never change again. In that case, an entirely new, complex life form will have emerged out of a simple set of rules. Even if small upgrades are implemented in the future, the 21 million coin supply cap is set in stone forever. Bitcoin is not for humans to have opinions about — it exists regardless of what anyone thinks about it, and it ought to be studied rather than discussed. We don’t know what true scarcity and a truly global, anonymous free market will do to our species yet, but we are about to find out. It is naïve to think otherwise. Various futurists and doomsday prophets have been focused on the dangers of the impending general artificial intelligence singularity lately, warning us about the point of no return, whereupon an artificial intelligence will be able to improve itself faster than any human could. Such a scenario could, as news anchor Ron Burgundy would have put it, escalate quickly. This may or may not be of real concern to us, but meanwhile, right under our noses, another type of unstoppable digital life has emerged, and it is already changing the behavior and preferences of millions of people around the globe. This is probably bad news for big corporations and governments but good news for the little guy looking for a little freedom. At least, that’s what those of us who lean towards the ideas of the Austrian school of economics believe. This time around, we will find out whether this is the case or not. No one knows what it will lead to and what new truths will emerge out of this new reality.
Unlike the termite, we humans are able to experience the grandeur of our progress. We can look in awe at the Sistine Chapel or the pyramids, and we can delve into the technicalities and brief history of Bitcoin and discover new ways of thinking about value along the way. Money is the language in which we express value to each other through space and time. Now, that language is spoken by computers. Value expressed in this language can’t be diluted through inflation or counterfeiting any longer. It is a language that is borderless, permissionless, peer-to-peer, anonymous (if you have the skills), unreplicable, completely scarce, non-dilutable, unchangeable, untouchable, undeniable, fungible, and free for everyone on Earth to use. It is a language for the future and it emerged out of a specific set of events in the past. All languages are examples of complex systems emerging out of simpler things, and Bitcoin evolved just as organically as any other human language did.
Decentralization is hard to achieve. Really hard. When it comes to claims of decentralization, a “don’t trust, verify” approach to the validity of such claims will help you filter out the noise. So, how can the validity of Bitcoin’s decentralization be verified? It’s a tricky question because decentralization is not a binary thing, like life or death, but rather a very difficult concept to define. However, the most fundamental concepts in Bitcoin, like the 21 million cap on coin issuance or the ten-minute block interval as a result of the difficulty adjustment and the Proof of Work algorithm, have not changed since very early on in the history of the network. This lack of change, which is arguably Bitcoin’s biggest strength, has been achieved through the consensus rules, which define what the blockchain is. Some special mechanisms (for example, BIP9) are sometimes used to deploy changes to the consensus rules. These mechanisms use a threshold when counting blocks that signal for a certain upgrade. For example, the upgrade “Segregated Witness” activated in a node when 95% or more of the blocks in a retarget period signaled support. Bitcoin has displayed a remarkable immutability through the years, and it is highly unlikely that this would have been the case if the game-theoretical mechanisms that enable its decentralized governance model hadn’t worked, given the many incentives to cheat that always seem to corrupt monetary systems. In other words, the longer the system seems to be working, the higher the likelihood that it actually does.
Satoshi set in stone the length of the halving period — a very important aspect of Bitcoin’s issuance schedule and initial distribution. During the first four years of Bitcoin’s existence, fifty new coins were issued every ten minutes up until the first block reward halving four years later. Every four years, this reward is halved so that the issuance rate goes down by fifty percent. This effectively means that half of all the Bitcoin that will ever exist was mined during the first four years of the network’s life, one fourth during its next four years, and so on. At the time of writing, we’re a little more than a year from the third halving. After that, only 6.25 Bitcoin will be minted every ten minutes as opposed to 50, which was the initial rate. What this seems to do is to create hype cycles for Bitcoin’s adoption. Every time the price of Bitcoin booms and then busts down to a level above where it started, a hype cycle takes place. Bitcoin had no marketing whatsoever, so awareness of it had to be spread through some other mechanism. When a bull run begins, people start talking about it, which leads to even more people buying due to fear of missing out (FOMO), which inevitably causes the price to rise even more rapidly. This leads to more FOMO, and on and on the bull market goes until it suddenly ends, and the price crashes down to somewhere around, or slightly above, the level it was at before the bull run started. Unlike what is true for most other assets, Bitcoin never really crashes all the way. Why? Because every time a hype cycle occurs, some more people learn about Bitcoin’s fundamentals and manage to resist the urge to sell, even when almost all hope seems lost. They understand that these bull markets are a reoccurring thing due to the nature of the protocol. These cycles create new waves of evangelists who start promoting Bitcoin simply because of what they stand to gain from a price increase. In a sense, the protocol itself pays for its own promotion in this way. This organic marketing creates a lot of noise and confusion, too, as a lot of people who don’t seem to understand how Bitcoin works are often very outspoken about it despite their lack of knowledge. Red herrings, such as altcoins and Bitcoin forks, are then weeded out naturally during bear markets. Every time a bull market happens, a new generation of Bitcoiners is born.
The four-year period between halvings seems to serve a deliberate purpose. Satoshi could just as well have programmed a smooth issuance curve into the Bitcoin protocol, but he didn’t. As events unfold, it seems that he had good reason for this since these hype cycles provide a very effective onboarding mechanism, and they seem to be linked to the halvings. They certainly make Bitcoin volatile, but remember that in this early stage, the volatility is needed in order for these hype cycles to happen. Later on, when Bitcoin’s stock-to-flow ratio is higher, the seas will calm, and its volatility level will go down. In truth, it already has. The latest almost 80% price drop was far from the worst we’ve seen in Bitcoin. This technology is still in its infancy, and it is very likely that we’ll see a lot more volatility before mainstream adoption, or hyperbitcoinization, truly happens.
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ bf95e1a4:ebdcc848
2025-04-11 11:18:42
@ bf95e1a4:ebdcc848
2025-04-11 11:18:42This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
An Immaculate Conception
Some concepts in nature are harder for us humans to understand than others. How complex things can emerge out of simpler ones is one of those concepts. A termite colony, for instance, has a complex cooling system at its lower levels. No single termite knows how it works. Completely unaware of the end results, they build complex mounds and nests, shelter tubes to protect their paths, and networks of subterranean tunnels to connect their dirt cities. Everything seems organized and designed, but it is not. Evolution has equipped the termite with a pheromone receptor that tells the termite what task he ought to engage himself in by simply counting the number of neighboring termites doing the same thing. If there’s a surplus of workers in an area, nearby termites become warriors, and so on. Complex structures emerge from simple rules. The fractal patterns found all around nature are another example. Fractals look complex, but in reality, they’re not. They’re basically algorithms — the same pattern, repeated over and over again with a slightly modified starting point. The human brain is an excellent example of a complex thing that evolved out of simpler things, and we humans still have a hard time accepting that it wasn’t designed. Religions, which themselves are emergent systems spawned out of human interaction, have come up with a plethora of explanations for how we came to be. All sorts of wild origin stories have been more widely accepted than the simple explanation that our complexities just emerged out of simpler things following a set of rules that nature itself provided our world with.
Complex systems emerge out of human interactions all the time. The phone in your pocket is the result of a century of mostly free global market competition, and no single human could ever have come up with the entire thing. The device, together with its internet connection, is capable of a lot more than the sum of its individual parts. A pocket-sized gadget that can grant instant access to almost all of the world’s literature, music, and film, which fits in your pocket, was an unthinkable science fiction a mere twenty years ago. Bitcoin, first described in Satoshi Nakamoto’s whitepaper ten years before these words were written, was designed to be decentralized. Still, it wasn’t until years later that the network started to show actual proof of this. Sound money, or absolute digital scarcity, emerged out of the network not only because of its technical design. How Bitcoin’s first ten years actually unfolded played a huge part in how true decentralization could emerge, and this is also the main reason why the experiment cannot be replicated. Scarcity on the internet could only be invented once. Satoshi’s disappearance was Bitcoin’s first step towards true decentralization. No marketing whatsoever and the randomness of who hopped onto the train first were the steps that followed. Bitcoin truly had an immaculate conception.
The network has shown a remarkable resistance to change over the last few years especially, and its current state might be its last incarnation given the size of the network and the 95% agreement threshold in its consensus rules. It might never change again. In that case, an entirely new, complex life form will have emerged out of a simple set of rules. Even if small upgrades are implemented in the future, the 21 million coin supply cap is set in stone forever. Bitcoin is not for humans to have opinions about — it exists regardless of what anyone thinks about it, and it ought to be studied rather than discussed. We don’t know what true scarcity and a truly global, anonymous free market will do to our species yet, but we are about to find out. It is naïve to think otherwise. Various futurists and doomsday prophets have been focused on the dangers of the impending general artificial intelligence singularity lately, warning us about the point of no return, whereupon an artificial intelligence will be able to improve itself faster than any human could. Such a scenario could, as news anchor Ron Burgundy would have put it, escalate quickly. This may or may not be of real concern to us, but meanwhile, right under our noses, another type of unstoppable digital life has emerged, and it is already changing the behavior and preferences of millions of people around the globe. This is probably bad news for big corporations and governments but good news for the little guy looking for a little freedom. At least, that’s what those of us who lean towards the ideas of the Austrian school of economics believe. This time around, we will find out whether this is the case or not. No one knows what it will lead to and what new truths will emerge out of this new reality.
Unlike the termite, we humans are able to experience the grandeur of our progress. We can look in awe at the Sistine Chapel or the pyramids, and we can delve into the technicalities and brief history of Bitcoin and discover new ways of thinking about value along the way. Money is the language in which we express value to each other through space and time. Now, that language is spoken by computers. Value expressed in this language can’t be diluted through inflation or counterfeiting any longer. It is a language that is borderless, permissionless, peer-to-peer, anonymous (if you have the skills), unreplicable, completely scarce, non-dilutable, unchangeable, untouchable, undeniable, fungible, and free for everyone on Earth to use. It is a language for the future and it emerged out of a specific set of events in the past. All languages are examples of complex systems emerging out of simpler things, and Bitcoin evolved just as organically as any other human language did.
Decentralization is hard to achieve. Really hard. When it comes to claims of decentralization, a “don’t trust, verify” approach to the validity of such claims will help you filter out the noise. So, how can the validity of Bitcoin’s decentralization be verified? It’s a tricky question because decentralization is not a binary thing, like life or death, but rather a very difficult concept to define. However, the most fundamental concepts in Bitcoin, like the 21 million cap on coin issuance or the ten-minute block interval as a result of the difficulty adjustment and the Proof of Work algorithm, have not changed since very early on in the history of the network. This lack of change, which is arguably Bitcoin’s biggest strength, has been achieved through the consensus rules, which define what the blockchain is. Some special mechanisms (for example, BIP9) are sometimes used to deploy changes to the consensus rules. These mechanisms use a threshold when counting blocks that signal for a certain upgrade. For example, the upgrade “Segregated Witness” activated in a node when 95% or more of the blocks in a retarget period signaled support. Bitcoin has displayed a remarkable immutability through the years, and it is highly unlikely that this would have been the case if the game-theoretical mechanisms that enable its decentralized governance model hadn’t worked, given the many incentives to cheat that always seem to corrupt monetary systems. In other words, the longer the system seems to be working, the higher the likelihood that it actually does.
Satoshi set in stone the length of the halving period — a very important aspect of Bitcoin’s issuance schedule and initial distribution. During the first four years of Bitcoin’s existence, fifty new coins were issued every ten minutes up until the first block reward halving four years later. Every four years, this reward is halved so that the issuance rate goes down by fifty percent. This effectively means that half of all the Bitcoin that will ever exist was mined during the first four years of the network’s life, one fourth during its next four years, and so on. At the time of writing, we’re a little more than a year from the third halving. After that, only 6.25 Bitcoin will be minted every ten minutes as opposed to 50, which was the initial rate. What this seems to do is to create hype cycles for Bitcoin’s adoption. Every time the price of Bitcoin booms and then busts down to a level above where it started, a hype cycle takes place. Bitcoin had no marketing whatsoever, so awareness of it had to be spread through some other mechanism. When a bull run begins, people start talking about it, which leads to even more people buying due to fear of missing out (FOMO), which inevitably causes the price to rise even more rapidly. This leads to more FOMO, and on and on the bull market goes until it suddenly ends, and the price crashes down to somewhere around, or slightly above, the level it was at before the bull run started. Unlike what is true for most other assets, Bitcoin never really crashes all the way. Why? Because every time a hype cycle occurs, some more people learn about Bitcoin’s fundamentals and manage to resist the urge to sell, even when almost all hope seems lost. They understand that these bull markets are a reoccurring thing due to the nature of the protocol. These cycles create new waves of evangelists who start promoting Bitcoin simply because of what they stand to gain from a price increase. In a sense, the protocol itself pays for its own promotion in this way. This organic marketing creates a lot of noise and confusion, too, as a lot of people who don’t seem to understand how Bitcoin works are often very outspoken about it despite their lack of knowledge. Red herrings, such as altcoins and Bitcoin forks, are then weeded out naturally during bear markets. Every time a bull market happens, a new generation of Bitcoiners is born.
The four-year period between halvings seems to serve a deliberate purpose. Satoshi could just as well have programmed a smooth issuance curve into the Bitcoin protocol, but he didn’t. As events unfold, it seems that he had good reason for this since these hype cycles provide a very effective onboarding mechanism, and they seem to be linked to the halvings. They certainly make Bitcoin volatile, but remember that in this early stage, the volatility is needed in order for these hype cycles to happen. Later on, when Bitcoin’s stock-to-flow ratio is higher, the seas will calm, and its volatility level will go down. In truth, it already has. The latest almost 80% price drop was far from the worst we’ve seen in Bitcoin. This technology is still in its infancy, and it is very likely that we’ll see a lot more volatility before mainstream adoption, or hyperbitcoinization, truly happens.
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ fd06f542:8d6d54cd
2025-04-11 11:15:10
@ fd06f542:8d6d54cd
2025-04-11 11:15:10Warning
unrecommended: deprecated in favor of NIP-27NIP-08
Handling Mentions
finalunrecommendedoptionalThis document standardizes the treatment given by clients of inline mentions of other events and pubkeys inside the content of
text_notes.Clients that want to allow tagged mentions they MUST show an autocomplete component or something analogous to that whenever the user starts typing a special key (for example, "@") or presses some button to include a mention etc -- or these clients can come up with other ways to unambiguously differentiate between mentions and normal text.
Once a mention is identified, for example, the pubkey
27866e9d854c78ae625b867eefdfa9580434bc3e675be08d2acb526610d96fbe, the client MUST add that pubkey to the.tagswith the tagp, then replace its textual reference (inside.content) with the notation#[index]in which "index" is equal to the 0-based index of the related tag in the tags array.The same process applies for mentioning event IDs.
A client that receives a
text_noteevent with such#[index]mentions in its.contentCAN do a search-and-replace using the actual contents from the.tagsarray with the actual pubkey or event ID that is mentioned, doing any desired context augmentation (for example, linking to the pubkey or showing a preview of the mentioned event contents) it wants in the process.Where
#[index]has anindexthat is outside the range of the tags array or points to a tag that is not aneorptag or a tag otherwise declared to support this notation, the client MUST NOT perform such replacement or augmentation, but instead display it as normal text. -
 @ fd06f542:8d6d54cd
2025-04-11 11:14:36
@ fd06f542:8d6d54cd
2025-04-11 11:14:36- 第三章、NIP-03: OpenTimestamps Attestations for Events
- 第四章、NIP-04: Encrypted Direct Message
- 第五章、NIP-05: Mapping Nostr keys to DNS-based internet identifiers
- 第六章、NIP-06: Basic key derivation from mnemonic seed phrase
- 第七章、NIP-07: window.nostr capability for web browsers
- 第八章、NIP-08: Handling Mentions --- unrecommended: deprecated in favor of NIP-27
-
 @ 7d33ba57:1b82db35
2025-04-11 10:08:21
@ 7d33ba57:1b82db35
2025-04-11 10:08:21Rome isn’t just a city—it’s a living, breathing museum where ancient ruins, baroque fountains, and buzzing piazzas come together in beautiful, chaotic harmony. Every cobblestone has a story, every espresso has a punch, and every sunset behind the Colosseum feels like a scene from a movie. Whether it's your first visit or your fifth, Rome never gets old.
🏛️ Top Things to See & Do in Rome
1️⃣ The Colosseum & Roman Forum
- Step inside the iconic arena of gladiators
- Wander through the ruins of the Forum, once the heart of ancient Rome
- Don’t miss Palatine Hill for views over it all
2️⃣ Vatican City
- Home to St. Peter’s Basilica, the Sistine Chapel, and the Vatican Museums
- Climb to the top of the basilica dome for one of the best panoramas in Rome
- Book tickets ahead—it gets packed!
3️⃣ Trevi Fountain
- Toss in a coin to ensure your return to Rome 💧
- Visit early in the morning or late at night to beat the crowds and get that perfect photo
4️⃣ Pantheon
- One of the best-preserved Roman temples—free to enter, awe guaranteed
- Look up: the open oculus in the dome is engineering genius
- Step outside for a coffee in Piazza della Rotonda
5️⃣ Piazza Navona & Campo de’ Fiori
- Piazza Navona: Elegant fountains, artists, street performers
- Campo de’ Fiori: Bustling morning market and lively nightlife
- Great spots to grab an aperitivo or soak up atmosphere
🍕 What to Eat in Rome
- Cacio e Pepe – Pasta with pecorino and black pepper—simple, bold, and pure Rome
- Carbonara – No cream! Just egg, cheese, guanciale, and pepper
- Supplì – Deep-fried rice balls with melted mozzarella inside
- Roman-style pizza – Thin and crispy, often sold by weight
- Gelato – Try real artisan shops like Gelateria del Teatro or Otaleg
🌇 Bonus Rome Moments
- Watch sunset from Pincian Hill or Gianicolo Terrace
- Stroll across the Tiber River to the charming Trastevere neighborhood
- Visit the Jewish Ghetto for history, architecture, and amazing food (hello, fried artichokes!)
- Wander without a map—Rome loves surprising you
🛵 Tips for Visiting
✅ Wear comfy shoes—Rome’s cobbles are beautiful, but brutal on feet
✅ Book major attractions in advance to skip lines
✅ Tap water is fresh—refill from Rome’s historic fountains (nasoni)
✅ Don’t rush—Rome is best enjoyed slowly, with a gelato in hand -
 @ fbf0e434:e1be6a39
2025-04-11 08:12:20
@ fbf0e434:e1be6a39
2025-04-11 08:12:20Hackathon 概要
Cambrian Hack 是一场最近的在线比赛,旨在吸引开发人员使用 Cambrian SDK 和 Jito Restaking 开发 Node Consensus Networks (NCNs)。此次活动吸引了88位注册开发人员,最终产生了九个批准项目。参与者专注于快速部署 NCN,探索如 AI 协处理器、预言机网络和区块链桥梁等应用。Hackathon 结束时,Cambrian 和 Jito 团队为前三名项目颁发了奖项。奖池的一部分包括 Cambrian 奖励 NFT,可以转换为 Cambrian 代币。
此次 Hackathon 强调了 Cambrian SDK 通过简化流程加速 NCN 开发的能力,减少了对大型团队的需求,并提供了预建组件。评估标准包括技术复杂性、市场潜力和创新性。
活动以在 Solana Apex 开普敦宣布获奖者而告终。Cambrian Hack 为开发者提供了与技术专家联系的机会,通过工作坊提升技能,并对 web3 和 Solana 生态系统的发展做出贡献。
Hackathon 获奖者
Cambrian NCN Builder 卓越奖获奖者
- Ping Project: 该项目通过在 Solana 区块链上使用 PoS 共识以及 Cambrian SDK 和 Jito Restaking 技术,强化网络完整性并管理奖励分配,提供去中心化的内容传递服务。
- Ant Vault: 结合 ElizaOS AI 代理与 Cambrian oracle 战略性管理 DeFi,提供智能化市场挑战解决方案。
- STABLE-FUNDS: Solana 上的平台,用于创建稳定币,集成去中心化预言机和质押机制,以连接政府支持的证券和 DeFi。
Cambrian 生态系统创新者奖获奖者
- NebulaCDN: 一种去中心化的内容传递网络,利用 Web3 技术提供高效且抗审查的数据分发。
- Kamui: 一个经济高效、安全的 Solana VRF oracle,旨在提供可靠且负担得起的随机性解决方案。
有关更多详情,请访问 Cambrian Hack BUIDL。
关于组织者
Cambrian
Cambrian 因其对技术和区块链发展的贡献而受到认可。该组织专注于创新区块链应用,已进行多项项目以提升数字基础设施。其成就包括与行业领袖合作开发安全高效的区块链系统。Cambrian 目前正在扩展其对去中心化技术的关注,努力提升不同平台的可访问性和安全性。通过其专业知识,Cambrian 在不断演变的技术和区块链产业中扮演着重要角色。
-
 @ fbf0e434:e1be6a39
2025-04-11 08:05:01
@ fbf0e434:e1be6a39
2025-04-11 08:05:01Hackathon 概要
Core Global Gaming Hackathon 圆满落幕。作为去中心化游戏领域的重要活动,其吸引了众多参与者。在 231 位注册开发者中,86 个项目获得批准,所有项目共同竞逐 38 万美元的奖金池。此次黑客松鼓励在 Bitcoin 与 Core 平台上进行游戏开发,着重强调去中心化游戏的创新。
活动通过激发参与者拓宽去中心化游戏开发的视野,催生出一系列创新参赛作品。它为开发者搭建了与活跃社区互动的平台,既能激发创意,也可能对游戏未来发展方向产生影响。
活动取得了显著成果,例如将 Core Chain 技术融入游戏应用,展现了利用去中心化平台的独特思路。2025 年 3 月 24 日,活动以 Demo Day 收官,现场展示最终项目并公布获奖者。总体而言,这场黑客松凸显了区块链技术在游戏领域的潜力,也体现了开发者们力求影响行业发展的合作精神。
Hackathon 获奖者
超休闲游戏奖获奖者
- Farming Saga:一款专注于建立农业帝国的策略和模拟游戏,特色为动态挑战和NFT整合以丰富游戏玩法。
- Zenista:一款闲置游戏,旨在通过经营虚拟水疗中心提供放松体验,设计用于提供自我护理体验。
- Market Magnate:一款零售模拟游戏,结合区块链实现真正的资产所有权,强调策略、创意和管理。
社交游戏PvP(玩家对玩家)奖获奖者
- Core Arena:一款PvP游戏,允许在战斗中使用任何ERC-721 NFT,并自动分配技能,促进NFT社区间的统一并延长项目生命周期。
- Fight For Tcore:一款基于区块链的实时PvP游戏,玩家参与双人对决并下注TCORE代币,利用智能合约实现去中心化游戏玩法。
- CoreVerse Battleground:一款实时多人区块链游戏,提供NFT交易和基于Core Blockchain的游戏内货币。
益智游戏奖获奖者
- Temporal Odyssey:一款基于区块链的益智游戏,提供跨越多样世界的解谜NFT奖励。
- Dungeon:提供程序生成的地牢探险体验,结合区块链元素,允许玩家将成就铸造成Dungeon Tokens ($DGN)。
- Skateflow:一款无尽滑板游戏,实施区块链技术实现潜在的游戏内奖励。
欲了解所有项目的更多详细信息,请访问Core Gaming Hackathon 页面。
关于组织者
Core DAO
Core DAO是一个专注于推进区块链技术的去中心化自治组织。其主要关注点在于增强去中心化和促进区块链生态系统中的社区驱动治理。Core DAO因其对开发创新共识机制和智能合约解决方案的贡献而受到认可。该组织采取重大措施以提高去中心化网络的可扩展性和安全性。目前,Core DAO致力于培育开放、包容的区块链环境,倡导技术进步,并支持社区主导的开发举措,以促进去中心化技术的全球采用。
-
 @ f57bac88:6045161e
2025-04-11 08:00:16
@ f57bac88:6045161e
2025-04-11 08:00:16مقدمه\ کتاب پول درهمشکسته نوشته لین الدن، یکی از برجستهترین آثار در زمینه اقتصاد و فناوری مالی است که در تابستان ۱۴۰۲ (۲۰۲۳ میلادی) منتشر شد. این کتاب با نگاهی عمیق به ریشههای پول، کاستیهای نظام مالی کنونی و ظرفیتهای فناوریهای نوین مانند بیتکوین، خوانندگان را به سفری فکری دعوت میکند. الدن با زبانی روان و دیدگاهی چندجانبه، پیچیدگیهای پول را به شکلی ساده اما پرمغز توضیح میدهد و به ما کمک میکند تا درک بهتری از چیستی پول، نقش آن در زندگی و آیندهاش به دست آوریم. این اثر ۵۳۸ صفحهای، با ساختاری جامع، گذشته، حال و آینده پول را در شش بخش اصلی بررسی میکند.
بخش اول: گذشته پول – از دفترهای قدیمی تا بانکداری نوین\ الدن داستان تکامل پول را در دو بخش ابتدایی کتاب روایت میکند. او پول را بهعنوان یک «دفتر حسابداری» معرفی میکند که از ابتدا برای ثبت بدهیها و طلبها در جوامع به کار میرفت. بخش اول به بررسی پولهای کالایی مانند صدف و فلزات گرانبها و ویژگیهای ایدهآل پول میپردازد. بخش دوم به ظهور خدمات بانکی اولیه و بانکداری گسترده اختصاص دارد و نشان میدهد که چگونه فناوریهایی مانند تلگراف در قرن نوزدهم تراکنشها را سریعتر کردند. اما این پیشرفتها، به گفته الدن، با متمرکز شدن کنترل پول در دست بانکهای مرکزی، اغلب به زیان مردم عادی تمام شدند و شکاف طبقاتی را عمیقتر کردند.
بخش دوم: حال پول – چرا سیستم مالی کنونی شکسته است؟\ در دو بخش بعدی، الدن به نقد نظام مالی کنونی میپردازد که بر پایه پول بیپشتوانه (فیات) بنا شده است. او استدلال میکند که این سیستم با مشکلاتی مانند تورم مداوم، نابرابری اقتصادی و سلطه بیشازحد نهادهای مالی دستبهگریبان است. بخش سوم به نظام مالی جهانی از اوایل قرن بیستم، از جمله نظام برتون وودز، میپردازد. بخش چهارم خلق پول مدرن و تأثیرات بدهیهای بیثباتکننده را تحلیل میکند. الدن معتقد است که پول بیپشتوانه بهگونهای طراحی شده که ارزش آن بهمرور کاهش مییابد و ثروت را از جیب مردم عادی بهسوی بانکها و شرکتهای بزرگ هدایت میکند. او با مثالهایی واقعی، مانند بحران اقتصادی لبنان در سال ۱۴۰۱ (۲۰۲۲) یا تورم افسارگسیخته در کشورهایی مانند ترکیه، آرژانتین و ایران، نشان میدهد که این مشکلات چگونه زندگی میلیونها نفر را تحت تأثیر قرار دادهاند.
بخش سوم: آینده پول – نقش نوآوریهای دیجیتال\ در دو بخش پایانی، الدن به بررسی فناوریهای نوین مالی، بهویژه بیتکوین و بلاکچین، میپردازد. بخش پنجم به نوآوریهای دیجیتال قرن بیستویکم، مانند بیتکوین، اختصاص دارد که الدن آن را یک دفتر حسابداری غیرمتمرکز میبیند. این فناوری میتواند قدرت را از نهادهای مرکزی خارج کرده و به افراد بازگرداند. بخش ششم به اخلاقیات پول و نقش رمزنگاری در شبکههای مالی میپردازد و آیندهای را تصور میکند که در آن افراد کنترل بیشتری بر داراییهای خود دارند. بااینحال، الدن به چالشهای بیتکوین، مانند نوسانات شدید قیمت، مصرف بالای انرژی و مشکلات مقیاسپذیری، نیز اشاره میکند. او همچنین به نمونههایی از استفاده بیتکوین در کشورهای درحالتوسعه، مانند السالوادور، اشاره دارد که این ارز بهعنوان ابزاری برای دور زدن محدودیتهای مالی به کار گرفته شده است.
نقاط قوت کتاب\ ۱. سادگی در عین عمق: الدن مفاهیم پیچیدهای مانند تورم، نظام بانکی و بلاکچین را با زبانی قابلفهم برای همگان توضیح میدهد، بدون آنکه از دقت علمی کاسته شود.\ ۲. دیدگاه چندرشتهای: او با ترکیب دانش مهندسی و تحلیل مالی، پول را بهعنوان یک فناوری بررسی میکند که با پیشرفتهای بشری تکامل مییابد.\ ۳. تمرکز بر انسانها: کتاب تنها به آمار و ارقام بسنده نمیکند؛ الدن نشان میدهد که نقصهای نظام مالی چگونه زندگی واقعی مردم را تحت تأثیر قرار داده است.\ ۴. بیطرفی نسبی: اگرچه الدن از طرفداران بیتکوین است، تلاش میکند با بررسی جنبههای مثبت و منفی هر سیستم، از یکجانبهگرایی پرهیز کند.
نقاط ضعف کتاب\ ۱. تمرکز بیشازحد بر بیتکوین: برخی معتقدند که الدن بیشازحد به بیتکوین خوشبین است و به دیگر فناوریهای مالی نوین، مانند اتریوم یا استیبلکوینها، کمتر پرداخته است.\ ۲. پیچیدگی برای تازهکارها: هرچند کتاب برای مخاطب عام نوشته شده، برخی بخشها ممکن است برای افرادی که هیچ آشنایی با اقتصاد یا ارزهای دیجیتال ندارند، دشوار باشد.\ ۳. کمبود راهحلهای عملی: الدن در شناسایی مشکلات موفق است، اما راهحلهای پیشنهادی او گاهی کلی و غیرملموس به نظر میرسند.
چرا این کتاب را بخوانیم؟\ پول درهمشکسته برای هرکسی که میخواهد بداند پول چیست، چرا ارزشش تغییر میکند و آیندهاش چه خواهد شد، یک راهنمای بینظیر است. این کتاب به ما کمک میکند تا به چیزهایی که بدیهی میپنداریم—مانند اسکناسی که هر روز خرج میکنیم—عمیقتر نگاه کنیم. برای خوانندگان ایرانی، که سالهاست با تورم، کاهش ارزش پول ملی و تحریمهای مالی دستوپنجه نرم میکنند، این کتاب پاسخهایی روشنگر به سؤالهایی مانند «چرا پول ما بیارزش میشود؟» یا «آیا راهی برای محافظت از داراییها وجود دارد؟» ارائه میدهد. ساختار ششبخشی کتاب، با پوشش جامع گذشته، حال و آینده، خواننده را به درک کاملی از پول و قدرت آن هدایت میکند.
جمعبندی\ پول درهمشکسته بیش از یک کتاب اقتصادی است؛ دعوتی است به تأمل و تغییر. لین الدن با دانش، دقت و نگاهی انسانی، ما را به سفری از گذشته پول تا آیندهاش میبرد و نشان میدهد که چگونه میتوانیم با آگاهی و انتخابهای درست، بهسوی سیستمی عادلانهتر حرکت کنیم. این کتاب برای هرکسی که به اقتصاد، فناوری یا عدالت اجتماعی علاقهمند است، اثری ضروری و الهامبخش به شمار میرود.
منابع و دسترسی به ترجمه\ بخشهایی از این کتاب به فارسی ترجمه شده و از طریق کانالهای تلگرامی مانند «ترجمهی مقالههای بیتکوین» در دسترس است. برای یافتن ترجمه، میتوانید عبارت «پول درهمشکسته» یا نام نویسنده را در این کانال جستجو کنید. همچنین، پیشنهاد میشود برای ادامه این مسیر و فرهنگ از مترجم و مدیر کانال ترجمه مقالات حمایت مالی کنید
-
 @ da0b9bc3:4e30a4a9
2025-04-11 07:02:54
@ da0b9bc3:4e30a4a9
2025-04-11 07:02:54Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/940429
-
 @ c1e9ab3a:9cb56b43
2025-04-11 04:41:15
@ c1e9ab3a:9cb56b43
2025-04-11 04:41:15Reanalysis: Could the Great Pyramid Function as an Ammonia Generator Powered by a 25GW Breeder Reactor?
Introduction
The Great Pyramid of Giza has traditionally been considered a tomb or ceremonial structure. Yet an intriguing alternative hypothesis suggests it could have functioned as a large-scale ammonia generator, powered by a high-energy source, such as a nuclear breeder reactor. This analysis explores the theoretical practicality of powering such a system using a continuous 25-gigawatt (GW) breeder reactor.
The Pyramid as an Ammonia Generator
Producing ammonia (NH₃) from atmospheric nitrogen (N₂) and hydrogen (H₂) requires substantial energy. Modern ammonia production (via the Haber-Bosch process) typically demands high pressure (~150–250 atmospheres) and temperatures (~400–500°C). However, given enough available energy, it is theoretically feasible to synthesize ammonia at lower pressures if catalysts and temperatures are sufficiently high or if alternative electrochemical or plasma-based fixation methods are employed.
Theoretical System Components:
-
High Heat Source (25GW breeder reactor)
A breeder reactor could consistently generate large amounts of heat. At a steady state of approximately 25GW, this heat source would easily sustain temperatures exceeding the 450°C threshold necessary for ammonia synthesis reactions, particularly if conducted electrochemically or catalytically. -
Steam and Hydrogen Production
The intense heat from a breeder reactor can efficiently evaporate water from subterranean channels (such as those historically suggested to exist beneath the pyramid) to form superheated steam. If coupled with high-voltage electrostatic fields (possibly in the millions of volts), steam electrolysis into hydrogen and oxygen becomes viable. This high-voltage environment could substantially enhance electrolysis efficiency. -
Nitrogen Fixation (Ammonia Synthesis)
With hydrogen readily produced, ammonia generation can proceed. Atmospheric nitrogen, abundant around the pyramid, can combine with the hydrogen generated through electrolysis. Under these conditions, the pyramid's capstone—potentially made from a catalytic metal like osmium, platinum, or gold—could facilitate nitrogen fixation at elevated temperatures.
Power Requirements and Energy Calculations
A thorough calculation of the continuous power requirements to maintain this system follows:
- Estimated Steady-state Power: ~25 GW of continuous thermal power.
- Total Energy Over 10,000 years: """ Energy = 25 GW × 10,000 years × 365.25 days/year × 24 hrs/day × 3600 s/hr ≈ 7.9 × 10²¹ Joules """
Feasibility of a 25GW Breeder Reactor within the Pyramid
A breeder reactor capable of sustaining 25GW thermal power is physically plausible—modern commercial reactors routinely generate 3–4GW thermal, so this is within an achievable engineering scale (though certainly large by current standards).
Fuel Requirements:
- Each kilogram of fissile fuel (e.g., U-233 from Thorium-232) releases ~80 terajoules (TJ) or 8×10¹³ joules.
- Considering reactor efficiency (~35%), one kilogram provides ~2.8×10¹³ joules usable energy: """ Fuel Required = 7.9 × 10²¹ J / 2.8 × 10¹³ J/kg ≈ 280,000 metric tons """
- With a breeding ratio of ~1.3: """ Initial Load = 280,000 tons / 1.3 ≈ 215,000 tons """
Reactor Physical Dimensions (Pebble Bed Design):
- King’s Chamber size: ~318 cubic meters.
- The reactor core would need to be extremely dense and highly efficient. Advanced engineering would be required to concentrate such power in this space, but it is within speculative feasibility.
Steam Generation and Scaling Management
Key methods to mitigate mineral scaling in the system: 1. Natural Limestone Filtration 2. Chemical Additives (e.g., chelating agents, phosphate compounds) 3. Superheating and Electrostatic Ionization 4. Electrostatic Control
Conclusion and Practical Considerations
Yes, the Great Pyramid could theoretically function as an ammonia generator if powered by a 25GW breeder reactor, using: - Thorium or Uranium-based fertile material, - Sustainable steam and scaling management, - High-voltage-enhanced electrolysis and catalytic ammonia synthesis.
While speculative, it is technologically coherent when analyzed through the lens of modern nuclear and chemical engineering.
See also: nostr:naddr1qqxnzde5xymrgvekxycrswfeqy2hwumn8ghj7am0deejucmpd3mxztnyv4mz7q3qc856kwjk524kef97hazw5e9jlkjq4333r6yxh2rtgefpd894ddpsxpqqqp65wun9c08
-
-
 @ d5c3d063:4d1159b3
2025-04-11 04:20:02
@ d5c3d063:4d1159b3
2025-04-11 04:20:02เศรษฐศาสตร์ออสเตรียน คืออะไร
“สูตร(ไม่)ลับ ที่รัฐไม่อยากให้คุณรู้”
ของแพงขึ้นทุกวัน เงินในกระเป๋าเหมือนมูลค่าหายไปเฉย ๆ คุณทำงานหนักขึ้น แต่ซื้อของได้น้อยลง แล้วก็ถูกสอนให้เชื่อว่า “นี่แหละ ทุนนิยม...”
แล้วถ้าทุนนิยมมันไม่ใช่แบบนี้ล่ะ แล้วถ้าทั้งหมดนี้ไม่ได้เกิดจาก “ตลาดล้มเหลว” แต่เป็นผลจากการที่มีใครบางคน…บิดเบือนตลาด
นั่นคือจุดเริ่มต้นของคำถาม ที่พาเราไปพบกับแนวคิดที่ชื่อว่า เศรษฐศาสตร์ออสเตรียน (Austrian Economics)
แนวคิดที่ดูเหมือนจะใหม่… แต่จริง ๆ แล้วมันคือ ความจริงเก่า ที่โลกพยายามลืม
จุดเริ่มต้นของการตั้งคำถาม
ปี 1871 ชายคนหนึ่งชื่อ Carl Menger
ตั้งคำถามกับความเชื่อของนักเศรษฐศาสตร์ในยุคนั้นว่า“ทำไมเพชรถึงแพงกว่าน้ำ ทั้งที่น้ำสำคัญกับชีวิต?”
เขาตอบว่า
“เพราะมูลค่าไม่ได้อยู่ในตัวสิ่งของ แต่มันอยู่ในมุมมองของแต่ละคน”
มันเปลี่ยนแปลงได้…แล้วแต่สถานการณ์ ความจำเป็น และเวลาแนวคิดนี้ชื่อว่า Subjective Value และกลายเป็นรากฐานของเศรษฐศาสตร์ออสเตรียน ซึ่งต่างจากเศรษฐศาสตร์กระแสหลักที่มองมูลค่าเป็นเรื่องตายตัว ที่คำนวณได้จาก “ต้นทุน + กำไร”
Menger ไม่ได้พูดเรื่องเงินหรือการลงทุน แต่เขากำลังพูดเรื่อง "มนุษย์" และ "เสรีภาพในการให้คุณค่าแก่สิ่งต่าง ๆ ด้วยตัวเอง"
มันไม่ใช่แค่เศรษฐศาสตร์ แต่มันคือ “ปรัชญาแห่งความเป็นมนุษย์”
แม้คำว่า “เศรษฐศาสตร์ออสเตรียน” จะเพิ่งมีเมื่อร้อยกว่าปีที่ผ่านมา แต่วิธีคิดแบบนี้…มีมานานกว่าพันปีแล้ว
โสเครติส แห่งเอเธนส์ เคยตั้งคำถามกับสิ่งที่รัฐบอกว่า “ถูกต้อง”
เหมือนที่เขาเคยเสนอให้เลิกรองเท้าไซส์เดียว เพราะมันไม่พอดีกับใครเลย เขาเชื่อว่า ความจริงไม่ควรถูกสอนให้ “เชื่อแบบไม่มีเหตุผล” แต่ต้อง “ถูกถาม ถูกสงสัย และถูกท้าทายเสมอ” และเพราะเขารู้ว่า...ไม่มีสิ่งใดเหมาะกับทุกคน โดยเฉพาะ “นโยบาย” ที่รัฐคิดแทนประชาชน
นี่แหละคือสิ่งเดียวกับที่เศรษฐศาสตร์ออสเตรียนเชื่อว่า ตลาดไม่ต้องการกฎที่ตัดเสื้อไซส์เดียวให้ทั้งสังคม แต่มันต้องการ “พื้นที่ให้คนเลือกได้ด้วยตัวเอง”
สโตอิก (Stoicism) เชื่อว่า เสรีภาพคือการควบคุมตัวเอง ไม่ใช่รอให้รัฐมากำกับ
สโตอิกไม่เคยบอกให้คน “ยอมรับชะตา” แบบจำนน แต่มันสอนว่า เสรีภาพที่แท้จริง เริ่มต้นจากการควบคุมตัวเอง ไม่ใช่จากการรอให้รัฐมากำกับหรือออกคำสั่งแทนชีวิตเรา
และนี่คือแนวคิดเดียวกับเศรษฐศาสตร์ออสเตรียน ที่เชื่อว่า “มนุษย์ทุกคนคือเจ้าของการกระทำของตนเอง” พฤติกรรมทางเศรษฐกิจไม่ได้เกิดจากสูตรหรือนโยบายบนกระดาษ แต่มันเกิดจาก “การตัดสินใจอย่างมีเหตุผล” ของคนธรรมดาที่ต้องเผชิญกับทางเลือกจริง ๆ
เช่นเดียวกับแนวคิด Human Action ของ Mises ที่มองว่าทุกการกระทำทางเศรษฐกิจคือ “การเลือก” ที่มีเหตุผลของแต่ละคน
ฝั่งตะวันออกอย่าง เต๋า (Taoism) ก็สอนว่า
“อย่าฝืนสิ่งที่สมดุลอยู่แล้ว”
เต๋าไม่ได้พูดแค่ “อย่าทำอะไร” แบบลัทธินิ่งเฉย แต่เต๋าบอกว่า การฝืน “ธรรมชาติ” ด้วยความไม่รู้...สร้างปัญหาเสมอ เหมือนตลาดที่ทำงานได้เอง ถ้าไม่มีใครไปควบคุมมัน
เศรษฐศาสตร์ออสเตรียน ก็เตือนว่าตลาดจะสมดุลได้ก็ต่อเมื่อ…ไม่มีใครพยายามควบคุมมัน
และ F.A. Hayek เองก็พูดชัดเจนว่า
“ข้อมูลในระบบเศรษฐกิจ ไม่ได้ถูกรวบไว้ในหัวคนเพียงไม่กี่คน แต่มันกระจายอยู่ในตัวของแต่ละปัจเจก ผ่านการตัดสินใจเล็ก ๆ ในแต่ละวัน” นั่นแปลว่า ไม่มีใคร ไม่ว่าจะเป็นนักการเมือง หรือผู้ว่าธนาคารกลาง จะเข้าใจโลกได้ดีกว่าคนที่ “ใช้ชีวิตอยู่ในโลกจริง ๆ”
เพราะเศรษฐกิจไม่ใช่สมการที่ใครคำนวณจบในห้องประชุม แต่มันคือ “กระบวนการกระจายของความรู้” ที่เกิดขึ้นจาก การซื้อ-ขาย-เลือก-ปฏิเสธ ของคนทุกคนในตลาด และเมื่อใดที่มีคนพยายามควบคุมสิ่งนี้จากส่วนกลาง... เมื่อนั้น ความพังย่อมตามมา
ปล่อยให้ตลาดทำหน้าที่ของมันเอง
เศรษฐศาสตร์ออสเตรียนเชื่อว่า - คนควรมีเสรีภาพในการซื้อ-ขายอย่างสมัครใจ
- ราคาที่เกิดจากการแลกเปลี่ยนโดยสมัครใจคือราคาที่แม่นยำที่สุด
- รัฐไม่ควรพิมพ์เงิน, ควบคุมราคา, หรือกำหนดดอกเบี้ยเพราะเมื่อไหร่ที่รัฐพยายาม “ควบคุมตลาด” นั่นคือจุดเริ่มของการบิดเบือน และจุดจบของคำว่า "เสรีภาพ"
ปัญหาที่เกิดขึ้นซ้ำซาก...ไม่ใช่อุบัติเหตุ แต่มันคือ “ระบบ”
Henry Hazlitt เคยเตือนไว้ตั้งแต่ปี 1947 ว่า
“เงินเฟ้อคืออาวุธเงียบที่รัฐใช้ทำลายระบบเศรษฐกิจ…แบบไม่มีใครรู้ตัว”
รัฐพิมพ์เงินเพื่อ “กระตุ้นเศรษฐกิจ” พอของแพงขึ้น…ก็โทษพ่อค้า โทษทุนนิยม แล้วก็ใช้เหตุผลว่า “เพื่อความมั่นคง เพื่อประชาชน เพื่อส่วนรวม” ในการออกกฎหมายควบคุมราคาหรือแจกเงินเพิ่ม
วงจรนี้...มันไม่ได้ใหม่เลย มันคือ สูตรเดิมที่รัฐใช้มาโดยตลอด และสุดท้ายคนธรรมดาอย่างเรา…ต้องจ่าย
แล้วเราจะทำยังไงละ...
คำตอบคือ…
“หยุดให้เขาควบคุมเรา ผ่านเงินที่พวกเขาพิมพ์ได้เอง”
นี่คือเหตุผลที่บิตคอยน์ไม่ใช่แค่เงินดิจิทัล แต่มันคือ “เศรษฐศาสตร์ออสเตรียนในรูปแบบที่ใช้ได้จริง”
- ไม่มีใครพิมพ์เพิ่มได้
- ไม่มีใครเปลี่ยนกติกากลางเกม
- ไม่มีธนาคารกลาง
- ไม่มีการช่วยเหลือเฉพาะกลุ่ม
- มีเพียง “คนที่ยินยอมแลกเปลี่ยนกัน โดยสมัครใจ” เท่านั้น
สรุป
เศรษฐศาสตร์ออสเตรียนไม่ใช่แค่แนวคิดทางเศรษฐกิจ แต่มันคือ “วิธีมองโลก” ที่เชื่อว่า..
- มนุษย์คือผู้กระทำที่มีเหตุผล
- ราคาคือผลของเสรีภาพ ไม่ใช่คำสั่ง
- และไม่มีใครควรควบคุมชีวิตคุณด้วยนโยบายที่คุณไม่ได้เลือก
มันอาจไม่ใช่แนวคิดใหม่ แต่มันคือ “ความจริงเก่า” ที่ทรงพลังที่สุดในโลกเสรี
Siamstr #เศรษฐศาสตร์สำนักออสเตรียน
-
 @ e17e9a18:66d67a6b
2025-04-11 03:03:13
@ e17e9a18:66d67a6b
2025-04-11 03:03:13We wrote this album to explain the inspiration behind Mutiny Brewing, and as a way to share the story of Bitcoin and freedom technologies like NOSTR. Through these songs, we’ve tried to capture every truth that we believe is essential to understand about money, freedom, trust, and human connection in the internet age. It’s our way of making these ideas real and relatable, and we hope it helps others see the power of taking control of their future through the systems we use.
01. "Tomorrow's Prices on Yesterday's Wage" explores the harsh reality of inflation. As central banks inflate the money supply, prices rise faster than wages, leaving us constantly falling behind. People, expecting prices to keep climbing, borrow more to buy sooner, pushing prices even higher in a vicious cycle. You're always a step behind, forced to pay tomorrow's inflated prices with yesterday's stagnant wages.
https://wavlake.com/track/76a6cd02-e876-4a37-b093-1fe919e9eabe
02. "Everybody Works For The Bank" exposes the hidden truth behind our fiat money system. When banks issue loans, they create new money from debt—but you must pay back both the principal and interest. That interest requires even more money, relying on others to borrow, creating an endless cycle of debt. If borrowing slows, the system falters and governments step in, printing more money to keep banks afloat. Ultimately, we’re all working to service debt, chained to the banks.
“Paying back what they create, working till I break” https://wavlake.com/track/4d94cb4b-ff3b-4423-be6a-03e0be8177d6
03. "Let My People Go" references Moses' demand for freedom but directly draws from Proverbs 6:1–5, exposing the danger of debt-based money. Every dollar you hold is actually someone else's debt, making you personally liable—held in the hand of your debtor and at risk of their losses, which you ultimately pay for through inflation or higher taxes. As the song says,_ "The more you try to save it up, the deeper in you get." _The wisdom of Proverbs urges immediate action, pleading urgently to escape this trap and free yourself, like a gazelle from a hunter.
https://wavlake.com/track/76214ff1-f8fd-45b0-a677-d9c285b1e7d6
04. "Mutiny Brewing" embodies Friedrich Hayek's insight: "I don't believe we shall ever have good money again before we take it out of the hands of government... we can't take it violently... all we can do is by some sly roundabout way introduce something they can't stop."
Inspired also by the Cypherpunk manifesto's rallying cry, "We will write the code", the song celebrates Bitcoin as exactly that unstoppable solution.
"Not here to break ya, just here to create our own little world where we determine our fate." https://wavlake.com/track/ba767fc8-6afc-4b0d-be64-259b340432f3
05. "Invisible Wealth" is inspired by The Sovereign Individual, a groundbreaking 1990s book that predicted the rise of digital money and explores how the return on violence shaped civilizations. The song references humanity's vulnerability since agriculture began—where stored wealth attracted violence, forcing reliance on larger governments for protection.
Today, digital privacy enabled by cryptography fundamentally changes this dynamic. When wealth is stored privately, secured by cryptographic keys, violence becomes ineffective. As the song emphasizes, "You can't bomb what you can't see." Cryptography dismantles traditional power structures, providing individuals true financial security, privacy, and freedom from exploitation.
“Violence is useless against cryptography” https://wavlake.com/track/648da3cc-d58c-4049-abe0-d22f9e61fef0
06. "Run A Node" is a rallying cry for Bitcoin's decentralisation. At its heart, it's about personal verification and choice: every node is a vote, every check’s a voice. By running the code yourself, you enforce the rules you choose to follow. This is true digital democracy. When everyone participates, there's no room for collusion, and authority comes directly from transparent code rather than blind trust.
"I verify, therefore I do." https://wavlake.com/track/ee11362b-2e84-4631-b05e-df6d8e6797f8
- "Leverage is a Liar" warns against gambling with your wealth, but beneath the surface, it's a sharp critique of fractional reserve banking. Fractional reserves inflate asset prices, creating the illusion of wealth built on leverage. This system isn't sustainable and inevitably leads to collapse. Real wealth requires sound money, money that can't be inflated. Trying to gain more through leverage only feeds the lie.
"Watch it burn higher and higher—leverage is a liar." https://wavlake.com/track/67f9c39c-c5e1-4e15-b171-f1f5442f29a5
- "Don't Get Rekt" serves as a stark warning about trusting custodians with your Bitcoin. Highlighting infamous collapses like Mt.Gox, Celsius, and FTX. These modern failures echo the 1933 Executive Order 6102, where the US government forcibly seized citizens' gold, banned its use, and then promptly devalued the currency exchanged for it. History shows clearly: trusting others with your wealth means risking losing it all.
"Your keys, your life, don't forget." https://wavlake.com/track/fbd9b46d-56fc-4496-bc4b-71dec2043705
- "One Language" critiques the thousands of cryptocurrencies claiming to be revolutionary. Like languages, while anyone can invent one, getting people to actually use it is another story. Most of these cryptos are just affinity scams, centralized towers built on shaky foundations. Drawing from The Bitcoin Standard, the song argues money naturally gravitates toward a single unit, a universal language understood by all. When the dust settles, only genuine, decentralized currency remains.
"One voice speaking loud and clear, the rest will disappear." https://wavlake.com/track/22fb4705-9a01-4f65-9b68-7e8a77406a16
- "Key To Life" is an anthem dedicated to NOSTR, the permissionless, unstoppable internet identity protocol. Unlike mainstream social media’s walled gardens, NOSTR places your identity securely in a cryptographic key, allowing you total control. Every message or action you sign proves authenticity, verifiable by anyone. This ensures censorship resistant communication, crucial for decentralised coordination around Bitcoin, keeping it free from centralised control.
"I got the key that sets me free—my truth is mine, authentically." https://wavlake.com/track/0d702284-88d2-4d3a-9059-960cc9286d3f
11. "Web Of Trust" celebrates genuine human connections built through protocols like Nostr, free from corporate algorithms and their manipulative agendas. Instead of top down control, it champions grassroots sharing of information among trusted peers, ensuring truth and authenticity rise naturally. It's about reclaiming our digital lives, building real communities where trust isn't manufactured by machines, but created by people.
"My filter, my future, my choice to make, real connections no one can fake." https://wavlake.com/track/b383d4e2-feba-4d63-b9f6-10382683b54b
12. "Proof Of Work" is an anthem for fair value creation. In Bitcoin, new money is earned through real work, computing power and electricity spent to secure the network. No shortcuts, no favourites. It's a system grounded in natural law: you reap what you sow. Unlike fiat money, which rewards those closest to power and the printing press, Proof of Work ensures rewards flow to those who put in the effort. Paper castles built on easy money will crumble, but real work builds lasting worth.
"Real work makes real worth, that's the law of this earth." https://wavlake.com/track/01bb7327-0e77-490b-9985-b5ff4d4fdcfc
13. "Stay Humble" is a reminder that true wealth isn’t measured in coins or possessions. It’s grounded in the truth that a man’s life does not consist in the abundance of his possessions. Real wealth is the freedom to use your life and time for what is good and meaningful. When you let go of the obsession with numbers, you make room for gratitude, purpose, and peace. It's not about counting coins, it's about counting your blessings.
"Real wealth ain't what you own, it's gratitude that sets the tone." https://wavlake.com/track/3fdb2e9b-2f52-4def-a8c5-c6b3ee1cd194
-
 @ 9a1adc34:9a9d705b
2025-04-11 01:59:19
@ 9a1adc34:9a9d705b
2025-04-11 01:59:19Testing the concept of using Nostr as a personal CMS.
-
 @ 3eba5ef4:751f23ae
2025-04-11 00:40:28
@ 3eba5ef4:751f23ae
2025-04-11 00:40:28Crypto Insights
2025 MIT Bitcoin Expo: Spotlight on Freedom Tech
The 12th MIT Bitcoin Expo took place on April 5–6, centering this year’s theme on “Freedom Tech” and how technology can facilitate physical and social liberation.
-
Day 1 Recap: Mawarire delivered the keynote speech “Why Freedom Tech Matters,” and Dryja discussed how Bitcoin demonstrates resilience against nation-states. The morning sessions focused on corporate adoption, featuring speakers such as Paul Giordano from Marathon Digital and Bitcoin Core contributors like Gloria Zhao. The afternoon shifted toward more technical topics, including consensus cleanup, poisoning attacks, censorship resistance, and the Bitcoin Pipes protocol.
-
Day 2 Recap: The focus shifted to global impact. Mauricio Bartolomeo discussed the exfiltration of resources via Bitcoin, followed by a panel with activists from Venezuela, Russia, and Togo. Technical topics included: scaling self-custody, Steven Roose’s covenant soft fork proposals, the future of freedom tech, quantum resistance, and Tor.
Into Bitcoin Address Poisoning Attacks
In this article, Jameson Lopp highlights the rise of Bitcoin address poisoning attacks—an emerging form of social engineering. Attackers send transactions from newly generated wallets that mimic the beginning and end characters of a target's recently used address. If the target later copies an address from their transaction history, they may unknowingly send funds to the attacker instead of the intended recipient. Though the success rate per attack is low, the low cost of transactions enables attackers to attempt thousands in a short period.
Lopp also argues that such attacks are a byproduct of low transaction fees and that higher fees could deter them. He also suggests wallet-level defenses, such as warnings like, “Oh, this came from a similar looking address,” to help users avoid interaction.
Examining the Mitigation Strategy Against Timewarp Attacks
Timewarp attacks, first identified around 2011, allow a majority of malicious miners to manipulate block timestamps, artificially lower difficulty, and mine blocks every few seconds. The “Great Consensus Cleanup” soft fork proposal can mitigate this by requiring that the first block in a new difficulty period must have a time no earlier than a certain number of minutes before the last block of the previous period.
A report examines the details of this BIP.
Tokenization on Bitcoin: Building a Global Settlement Layer with Taproot Assets and Lightning
Bitcoin’s evolution into a multi-asset platform is accelerating with the advent of Taproot Assets and Lightning Network. The integration of these technologies combines Bitcoin’s decentralization and security with the speed and scalability of the Lightning Network. This report examines how Taproot Assets enable asset issuance, transfers, and swaps on Bitcoin’s base layer, and how the Lightning Network facilitates fast, low-cost transfers of those assets. We compare this approach to earlier attempts at Bitcoin asset issuance and analyze its market potential against other blockchains and traditional payment networks.
Solving Data Availability in Client-Side Validation With UTxO Binding
Issuing tokens on Bitcoin is attractive due to its security and dominance, but its limited functionality creates challenges. Client-side validation (CSV) is a common workaround, using off-chain data with on-chain verification, though it risks data loss and withholding. This paper introduces UTxO binding, a framework that links a Bitcoin UTxO to one on an auxiliary chain, providing data storage and programmability. The authors prove its security and implement it using Nervos CKB.
From State Differences to Scaling: Citrea’s Fee Mechanism for Bitcoin
The Citrea team has designed a new fee mechanism to enhance Bitcoin’s scalability without compromising security. It only records essential state differences (i.e., state slot changes) on the Bitcoin main chain, using zero-knowledge proofs to ensure verifiability and Bitcoin security while drastically reducing state inscription costs. Optimizations include: replacing
codefield withcode_hash, compressing state data using a highly efficient compression algorithm Brotli, and analyzing historical Ethereum block data to estimate each transaction’s impact on cumulative state differences—enabling a discount to each transaction.Second: A New Ark Implementation Launched on Bitcoin Signet
Second, a protocol based on Ark to improve Bitcoin transaction throughput, has launched Bark, a test implementation on Bitcoin Signet.
Ark makes Bitcoin transactions faster, cheaper, and more private, allowing more users and transactions per block. However, funds stored non-custodially via Ark can expire if unused, making it slightly less trustless than mainchain transactions.
BitLayer Optimizes BitVM Bridge Protocol and Demonstrates on Testnet
Bitlayer BitVM Bridge protocol is an optimized adaptation of the bridge protocol outlined in the BitVM2 paper, to improve efficiency, scalability, and security—especially for high-risk cross-chain transactions.
In this article, two key testnet demos on bitvmnet (a BitVM-dedicated testnet) demonstrate how the protocol can:
-
Effectively thwart fraudulent reclaim attempts by brokers.
-
Protect honest brokers from malicious or baseless challenges.
Cardano Enables Bitcoin DeFi via BitVMX and Lightning Hydra
Cardano is integrating with Bitcoin through Lightning Hydra and BitVMX to enable secure and scalable Bitcoin DeFi.
Zcash’s Tachyon Upgrade: Toward Scalable Oblivious Synchronization
Zcash has unveiled project Tachyon, a proposal to scale Zcash by changing how wallets sync and prove ownership of notes. Instead of scanning the entire blockchain, wallets track only their own nullifiers and receive succinct proofs from untrusted, oblivious sync servers. Transactions include proofs of wallet state (using recursive SNARKs), allowing nodes to verify them without keeping the full history. Notes are exchanged out-of-band, reducing on-chain data and improving privacy. In the nominal case, users get fast sync, lightweight wallets, and strong privacy, without the need to trust the network.
Podcast | Why the Future of Bitcoin Mining is Distributed
In this podcast, Professor Troy Cross discusses the centralization of Bitcoin mining and argues convincingly for hashrate decentralization. While economies of scale have led to mega mining operations, he sees economic imperative that will drive mining toward a globally distributed future—not dominated by the U.S.—ensuring neutrality and resilience against state-level threats.
Binance Report|Crypto Industry Map March 2025
This report provides an overview of projects using a framework that divides crypto into four core ecosystems—Infrastructure, DeFi, NFT, and Gaming—and four trending sectors: Stablecoins, RWA, AI, and DeSci.
For infrastructure, five key pillars are identified: scalability & fairness, data availability & tooling, security & privacy, cloud networks, and connectivity. The report also maps out and categorizes the major projects and solutions currently on the market.

Top Reads on Blockchain and Beyond
A Game-Theoretic Approach to Bitcoin’s Valuation in Equilibrium
The author presents a game-theoretic argument for why Bitcoin will emerge as the optimal unit of account in equilibrium. The argument is based upon the observation that a generally agreed upon unit of account that represents a constant share of total wealth (equal to the totality of all other economic utility) will naturally create price signals that passively stabilize the macroeconomy, without requiring external intervention.
Bitcoin’s unique properties—finite supply, inertness, fungibility, accessibility, and ownership history—position it as the leading candidate to emerge as this unit.
Neo: Lattice-Based Folding Scheme for CCS Over Small Fields and Pay-Per-Bit Commitments
This paper introduces Neo, a new lattice-based folding scheme for CCS, an NP-complete relation that generalizes R1CS, Plonkish, and AIR. Neo's folding scheme can be viewed as adapting the folding scheme in HyperNova (CRYPTO'24), which assumes elliptic-curve based linearly homomorphic commitments, to the lattice setting. Unlike HyperNova, Neo can use “small” prime fields (e.g., over the Goldilocks prime). Additionally, Neo provides plausible post-quantum security.
Social Scalability: Key to Massive Value Accumulation in Crypto
Social scalability, a concept first proposed by Nick Szabo in his 2017 article Money, Blockchains, and Social Scalability, is further explored in this thread. Here, “social scalability” refers to an institution's ability to allow the maximum number of people to have skin in the game and win. It’s seen as the main reason crypto has become a $2.9T asset class today and a key driver of value accumulation in the coming decade.
The author argues that two critical ingredients for long-term social scalability are credible neutrality and utility. Currently, only BTC and ETH have this potential, yet neither strikes a perfect balance between the two. The author notes that there is not yet a strong narrative around social scalability, and concludes by emphasizing the importance of focusing on long-term value and resisting the temptation of short-term market narratives.
-
-
 @ 3eba5ef4:751f23ae
2025-04-11 00:37:33
@ 3eba5ef4:751f23ae
2025-04-11 00:37:33加密洞见
2025 MIT Bitcoin Expo:关注自由科技
第 12 届 MIT Bitcoin Expo 在 4 月 5 - 6 日举行。今年的议题围绕 Freedom Tech 探讨通过技术实现物理解放。
-
Day 1 概览:Mawarire 发表主题演讲「为什么自由科技很重要」,Dryja 分析了比特币如何在国家力量面前展现韧性。上午的讨论聚焦于企业采用,由 Marathon Digital 的 Paul Giordano 和 Bitcoin Core 开发者如 Gloria Zhao 主讲。下午转入技术性议题,包括:共识机制清理、投毒攻击(poisoning attacks)、抗审查能力、Bitcoin Pipes 协议等。
-
Day 2 概览:全球影响。Mauricio Bartolomeo 介绍如何通过比特币进行数据外传,另有来自委内瑞拉、俄罗斯、多哥的活动家参与小组讨论。而技术环节的讨论涉及了:自托管的扩展、限制条款软分叉提案、自由技术的未来、抗量子攻击、Tor 等。
比特币地址中毒攻击调查
Jameson Lopp 在本文中指出,比特币地址投毒攻击(address poisoning attacks)正在增加。这种攻击属于社会工程,攻击者向目标发送来自新生成的钱包的交易——该钱包的第一个和最后一个字符与目标钱包匹配,或来自目标最近与之交互的钱包。下次目标想要向该钱包汇款时,可能会错误地从交易历史记录中复制相似的地址,并直接将钱汇给黑客,而不是他们的预期收款人。虽然地址中毒攻击一次成功的几率较低,但低交易费用可以在相对较短的时间内执行数千次攻击。
他还认为这种攻击是一个极低费率环境所导致的,所以若收取较高费用,可以极大地抑制此类攻击。此外,他认为在钱包设计上,可以显示警告,如提示:「这笔交易来自一个看起来相似的地址」,并建议用户不要与之互动。
对解决「时间扭曲攻击」的软分叉策略的评估
时间扭曲攻击在 2011 年左右首次被发现,它可以使大多数恶意矿工可以操纵区块时间戳、任意降低难度,并每隔几秒钟开采一个区块。该攻击可以通过「共识清理」(Great Consensus Cleanup)软分叉解决——通过要求新难度周期中的第一个区块的时间不早于前一个周期中最后一个区块之前的 X 分钟。
本报告详细研究了该 BIP 建议的修复程序。
比特币上的代币化:用 Taproot Assets 和 Lightning 构建全球结算层
随着 Taproot Assets 和闪电网络的出现,比特币正在加速向多资产平台的演变 。这些技术的集成将比特币的去中心化和安全性与闪电网络的速度和可扩展性相结合。本报告研究了 Taproot Assets 如何在比特币的基础层上实现资产发行、转移和交换,以及闪电网络如何促进这些资产的快速、低成本转移,并将这种方法与早期的比特币资产发行尝试进行了比较,分析了其与其他区块链和传统支付网络的市场潜力。
用 UTxO 绑定,解决客户端验证中的数据可用性限制
在比特币上发行代币具有吸引力,原因在于其安全性和主导地位,但其功能受限也带来了不少挑战。客户端验证(CSV)是一种常见的解决方案,它结合链下数据与链上验证,但存在数据丢失或数据被恶意扣留的风险。本论文提出了一种名为vUTxO 绑定的框架,用于将比特币上的一个 UTxO 与辅助链上的一个 UTxO 关联起来,从而实现数据存储和可编程性。作者还对该方案的安全性进行了形式化证明,并通过 Nervos CKB 实现了该框架。
从状态差异出发:Citrea 重构比特币的收费机制
Citrea 团队设计出一种收费机制,旨在在不牺牲安全性的前提下提升比特币的可扩展性。该机制仅在比特币主链上记录必要的状态差异(即状态槽的变化),并使用零知识证明来确保可验证性和比特币级别的安全性,同时大幅降低状态写入的成本。优化措施包括:用
code_hash替代原有的code字段、使用高效的压缩算法 Brotli 压缩状态数据、并通过分析以太坊历史区块数据来估算每笔交易对状态差异累积的影响,从而为每笔交易提供费用折扣。Second:新的 Ark 实现在比特币 Signet 上启动
Second 是一个基于 Ark 设计 的协议,旨在提升比特币的交易吞吐能力,已在 Bitcoin Signet 上推出测试实现 —— Bark。
Ark 让比特币交易更快、更便宜、更隐私,支持更多用户和更多交易纳入每个区块。然而,通过 Ark 非托管方式存储的资金若长时间未使用,可能会过期,这使得其在信任最小化方面略逊于主链交易。
BitLayer 优化了 BitVM 桥协议,并展示两个测试网案例
Bitlayer 的 BitVM Bridge 协议是对 BitVM2 论文 中桥接协议的优化改进,旨在提升效率、可扩展性和安全性,尤其是针对高风险的跨链交易。
本文展示了两个在 bitvmnet(一个专为 BitVM 设立的测试网络)上的测试用例,展示该协议如何:
-
有效阻止经纪人的欺诈性回收尝试
-
保护诚实经纪人免受恶意和毫无根据的挑战
Cardano 通过 BitVMX 和 Lightning Hydra 启用比特币 DeFi
Cardano 正在通过 Lightning Hydra 和 BitVMX 与比特币集成,实现安全且可扩展的比特币 DeFi。
Zcash 的 Tachyon 隐私升级提案:迈向可扩展的「无感同步」
Zcash 推出了名为 Tachyon 的新项目提案,旨在通过改变钱包同步和笔记所有权验证方式来扩展 Zcash。该方案不再要求钱包扫描整个区块链,而是只追踪自己的 nullifier,并从不可信、无状态的同步服务器接收简洁的证明。交易中包含钱包状态的证明(基于递归 SNARK),使节点无需保存完整历史即可验证交易。笔记的交换在链下完成,从而减少链上数据并增强隐私。在理想场景下,用户将获得快速同步、轻量级钱包和强隐私性,无需信任网络本身。
播客|为什么比特币挖矿的未来是分布式的
Troy Cross 教授在《为什么比特币挖矿的未来是分布式的》(Why the Future of Bitcoin Mining is Distributed)采访中,讨论了当前比特币挖矿中的中心化的原因,并为哈希率的去中心化提出了令人信服的论点。尽管规模经济催生了大型采矿业务,但他强调存在有某种经济驱动力,会推动采矿权的分散化。他认为比特币挖矿的未来是全球分步的,而非美国主导,确保其中立性和价值免受民族国家攻击。
币安报告|2025 三月行业地图
本报告以 crypto 的四个核心生态(基础设施、DeFi、NFT、游戏)和四个热门领域(稳定币、RWA、AI、DeSci)为框架,提供了一份项目概览。
基础设施的五大要素被认为是:可扩展性和公正、数据可用性和工具、安全和隐私、云网络、链接性。报告也就目前市面上的各特定项目和解决方案做了梳理和归纳。

精彩无限 不止于链
比特币均衡估值的博弈论方法
本文提出了一个博弈论视角的论证,说明为什么比特币最终将在均衡状态下成为最优的记账单位。该论证基于这样一个观察:一种被普遍接受、能够代表总财富恒定份额(等同于其他所有经济效用总和)的记账单位,将自然地形成价格信号,从而被动地稳定宏观经济,而无需外部干预。
比特币所具备的独特属性——供应有限、惰性强、可替代性强、可访问性高,以及清晰的所有权历史,使其成为最有可能演化为这种记账单位的候选者。
Neo: 基于格的折叠方案 —— 用于小域上的可定制约束系统与按比特付费的承诺机制
本论文介绍了 Neo —— 一种基于格的新折叠方案,适用于 CCS(Customizable constraint systems)。它是一个推广了 R1CS、Plonkish 和 AIR 的 NP 完全关系。Neo 折叠方案可以看作是将 HyperNova(CRYPTO'24)中的折叠方案从椭圆曲线下的线性同态承诺模型迁移到格设定下。但与 HyperNova 不同,Neo 能够使用「小」素域(如 Goldilocks 素数),并且具备可信的抗量子安全性。
社交可扩展性:加密领域巨大价值积累的关键
社交可扩展性(Social scalability)最初是由 Nick Szabo 在 2017 年的《Money, Blockchains and Social Scalability》一文中提出的。而这篇推文在此观点上作了延展,此处的「社交可扩展性」指一个机构允许最大数量的人参与游戏并获胜的能力,它是加密货币今天成为 $2.9T 资产类别的主要原因,并且将在未来十年带来巨大的价值积累。
作者认为实现长期社交可扩展性的两个关键是:可信中立性和有用性,而目前只有 BTC 和 ETH 具有这样的能力,但它们依然没有很好地兼顾两者;社交可扩展性目前还没有一个强有力的叙事。文章最后强调,专注于长期价值并抵制短期市场叙事的诱惑是非常重要的。
-
-
 @ 378562cd:a6fc6773
2025-04-11 00:02:38
@ 378562cd:a6fc6773
2025-04-11 00:02:38What Happens When You Wean Your Digital Life Way Back?
We’re swimming in screens. Notifications, news, and endless feeds are all designed to keep us plugged in, distracted, and running on digital fumes. But what happens when you stop feeding the machine?
What happens when you step back, shut it off, and just… live?
You might be amazed.
Step One: Wean Way Down
Start simple. No grand declarations, but just a quiet rebellion.
Fewer apps. Fewer tabs. Less time online. Maybe you only use the computer in the mornings. Maybe you can turn your phone off in the evening. Maybe Sunday will become a screen-free Sabbath.
The goal? Clear. Clean. Quiet.
At first, it might feel weird. Like quitting sugar or coffee, you’ll feel the pull. But then? Something shifts.
What Starts to Happen… 1. Your Mind Clears Up You stop bouncing from thought to thought. You breathe. You remember what it feels like to think deeply, uninterrupted. Your brain stops buffering and starts building again.
-
Time Slows Down You realize how much time was slipping through your fingers. Without the digital drag, you suddenly have space. You get stuff done. You notice the birds. You fix the fence. You write a letter. You rest. I've personally done these things. It IS AMAZING!
-
You Hear God More Clearly When the digital static dies down, the whisper of God gets louder. Scripture comes alive again. Prayer feels less like a chore and more like a lifeline. You hear Him in the quiet—and sometimes, even in yourself.
-
People Come Back into Focus You stop skimming people like headlines. You sit down, look up, listen, and be present. You find yourself reaching out more, talking longer, and remembering what a real connection feels like.
-
You Feel Alive Again You get energy back, your hands get busy with real work, your body moves, and your sleep deepens. You feel stronger, clearer, and more grounded like your soul has room to breathe again.
It’s Not About Losing—It’s About Gaining Less screen time isn’t about guilt or rules. It’s about freedom. It’s about trading mindless digital noise for something deeper, like clarity, creativity, peace, and presence.
Will you miss some stuff? Sure. But what you’ll gain is real life. Good life.
Try it. Wean way down. Scale Back! Watch what happens.
-
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-10 23:42:56
@ 5d4b6c8d:8a1c1ee3
2025-04-10 23:42:56In another team up with Global Sports Central, we are going to do a bracket challenge for the NBA Playoffs.
They've gotten their hands on a special prize from Blockstream to award the winner and they're hoping that Stackers will take part in the contest.
We're still working out all the details, but there will likely be a small buy-in and the runner up in the contest will win those sats.
The NBA Play-In Tournament, that determines final seeding, starts on April 15th. Once the seeding is set, we'll open up the contest for people to submit their brackets from NBA Bracketology.
Start thinking about your brackets now and make your bracketology account, so you can walk away with one of the prizes.
Also, let us know your thoughts about how big the buy-in should be. We want to discourage people from spamming a bunch of brackets without discouraging those who want to take part in the contest.
https://primal.net/e/nevent1qvzqqqqqqypzqpqrep4phdx0hs6v3fynl0glp52c6skaqmgra23hyzyz5pnd8gmcqqsw33tk6puje8ceq4uyymssmgesskqrll8elua7ldfdftr05lts30sx32z65
originally posted at https://stacker.news/items/940274
-
 @ 9226eda1:6a1bde0e
2025-04-10 23:42:02
@ 9226eda1:6a1bde0e
2025-04-10 23:42:02Hi from Comet Notes!
const impressed = true;https://www.youtube.com/watch?v=JRnDYB28bL8
comet #notes
-
 @ 9226eda1:6a1bde0e
2025-04-10 23:42:00
@ 9226eda1:6a1bde0e
2025-04-10 23:42:00Hi from Comet Notes!
const impressed = true;https://www.youtube.com/watch?v=JRnDYB28bL8
comet #notes
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-10 23:05:11
@ 5d4b6c8d:8a1c1ee3
2025-04-10 23:05:11So, we've been trying to housebreak this dog (that was supposedly already housebroken). We had gone out first thing in the morning, but she didn't poop. I figured the poop accident she had had right before bed might be the reason. Maybe she just had nothing left in the tank.
Well, no. While I was getting dressed, she was quickly dropping a deuce on the carpet. I cleaned that up and headed out for a while. Apparently, she pooped again while I was gone, despite being let out several times.
Then, upon my return, as my wife is telling me about the dog's accidents, the kid comes running inside shouting " I POOPED MY PANTS!" What's happening?
We get her into the bath, scrub her down, and get her all cleaned up. I take another attempt at finishing my dinner, only to hear some indecipherable shouting from upstairs. Of course it's more poop. The kid is sitting on the toilet screaming about getting poop on her hands while trying to wipe.
Finally, I took the dog out for a walk to hopefully avoid another poop incident...and the leash snapped.
originally posted at https://stacker.news/items/940243
-
 @ 000002de:c05780a7
2025-04-10 22:22:41
@ 000002de:c05780a7
2025-04-10 22:22:41From time to time I will listen to a podcast called "The Dangerous History Podcast" and in the most recent episode he plays some "music" from the WW1 propaganda machine. Its wild how on the nose it is. I think people forget how in your face propaganda was in the past. Its more subtle today and people sometimes act as if news, media and entertainment were once reliable sources of information. When I hear people complaining about bias or propaganda in media today I usually push back and say, its better than it was in the past. At least now we have more choice as well as tools to check things for ourselves.
Don't forget, the state has always been about manipulating you. Sure, it changes its tactics but there really isn't some golden era where this wasn't happening. They have just become more sophisticated as the people get more keen on the old tactics.
originally posted at https://stacker.news/items/940221
-
 @ 8d5ba92c:c6c3ecd5
2025-04-10 22:20:40
@ 8d5ba92c:c6c3ecd5
2025-04-10 22:20:40It’s often said that 'Bitcoin doesn’t need marketing'—and the internet proves it well, almost like a daily feed. Instead of typical ads in the form of 'sell-me-anything-and-everything', the space thrives on organic memes and threads: a grassroots testament to Bitcoin ethos.
This isn’t about the artificial promotion of THE TRUMAN SHOW, where desires are manufactured and ads dictate specific behaviours. Bitcoiners don’t just reject the Proof-of-Hype, so typical in a fiat-driven world, they replace it with Proof-of-Work: value emerging not from coercion, but from consensus (i.e., what the community validates as genuine and meaningful).
The "Funny Money" Crew
On the other hand, equally common is the twist with memes labeled 'Bitcoin’s Marketing Team', featuring faces like:
🤡 Jerome Powell (Fed Chair), Christine Lagarde (ECB), Agustín Carstens (BIS chief, CBDC pusher), Janet Yellen (U.S. Treasury Secretary), Jamie Dimon (JPMorgan CEO), Elizabeth Warren (U.S. Senator), and so on.
Sophisticated jokes—appreciated by those who understand their actual impact. After all, what better advertisement for Bitcoin could there be than watching the fiat system degrade in real time? 😎
Why Bring This Up?
First, because I want to remind that Bitcoiners weaponize even simple ideas better than entire Wall Street-hired PR firms. Every "Bitcoin doesn’t need marketing" or "Thanks, Fed for the free promo!" is a clever, almost subversive way of raising topics we should be aware of. Exposing fiat’s failures often speaks louder than directly evangelizing how sound Bitcoin is—and how well it solves problems that keep many non-coiners awake at night.
Second, to credit where it’s due: Bitcoin-only projects and individuals who are actively spreading the word—hard money, real solutions, and the culture itself. But this isn’t 'marketing' in the traditional, pushy, profit-at-all-costs sense. Instead, it’s built on:
- Information (no bullshit, just facts)
- Education (orange-pilling, not upselling)
- Community (value, instead of dry PR)
- Creativity (proof-of-mind, not algo-baits)
- Experiences (how-to solutions, not showing off)
And let’s be clear: Earning money isn’t evil—it’s necessary for these projects to survive. What matters is the intention. No one should apologize for creating Bitcoin-themed ads, so long as they’re carrying the meaning, instead of being rooted in hype.
PoW: Earning Attention, Not Buying It
The list below (part one) is based on my own preferences, but it was also inspired by Bitcoin FilmFest, which—in its upcoming edition #BFF25, May 22-25—introduced a new block to the program: ‘BFF PoWies: The Show for Bitcoin-Only Advertising.’ A dedicated space for creative expression beyond films, where projects and individuals compete for awards in categories like Grand Prix, Best Visual, and Best Identity—with a $4,500 prize pool to grab.
Anyways, as our small but passionate team dug into this topic, I was really happy to uncover unique video ads, some of which I’m excited to share with you now.
If you know others, tag me (private profile) or 'Bitcoin FilmFest' directly on socials. Feel free to submit your work to the PoWies too (submissions close May 6th).
Without further ado... Let's explore the space where value is discovered, not packaged in empty promises 📺👇
Bitcoin-Video Ads: Part One.
Creative, funny, dynamic, inspirational. All four below. Enjoy!
1/. NEVER LOSE YOUR BITCOIN (Liana)
https://v.nostr.build/P7To0HpNmmB6iudR.mp4
2/. MAKE A CHANGE, (Wasabi)
https://v.nostr.build/rUGQAysAIDH8Wx9x.mp4
3/. THE MOTHER OF ALL BACKUPS (Cryptosteel)
https://v.nostr.build/3zesnSjQudQoxl5f.mp4
- FINANCIAL FALLOUT (21 Futures)
https://v.nostr.build/sFvmt8oCWfxLKJRb.mp4
PS. The most effective Bitcoin ads aren't 'typical' campaigns—they're the result of creativity, PoW, and authentic storytelling move hand-in-hand.
BTC Your Mind. Let it Beat... Şela
-
 @ 5677fa5b:15a5d3e1
2025-04-10 21:14:26
@ 5677fa5b:15a5d3e1
2025-04-10 21:14:26https://www.spglobal.com/ratings/en/research/articles/250327-cryptocurrency-is-growing-within-u-s-state-reserves-and-statewide-pension-plans-13455336
I've watched pension plans repeatedly fumble the ball over the past 30 years. In the 80s and 90s they were run, not by CFOs, but out of Human Resources by nonfinancial officers who repeatedly enriched the benefits during an era of double-digit interest rates which had the liabilities so low that companies weren't allowed to contribute to them. Once CFO's figured out what they inherited, they continued to ignore the fix because their worldview was the risk-ignorant FAS87 accounting standard that incentivized risk maximization by allowing immediate recognition of expected returns while smoothing upon smoothing the volatility in the future. Even the smarter ones who adopted Liability Driven Investing ( LDI) eventually discovered their ruin by borrowing against their unrealized gains only to cause a liquidity crisis in 2022 when the UK gilts spiked out of control, necessitating a $60B bailout from the Bank of England.
It is a nonstop series of loss and dysfunction. Now "cryptocurrency" is entering the scene as if to offer the industry one last chance they don't deserve to snatch victory from the claws of defeat. If, by cryptocurrency, one means Bitcoin, then we might have a fighting chance still in this game. If one means any of the other altcoins, then they might as well pack their bags and surrender before they commit a worse offense than Canada's OTTP plan, who directed $100 million of its pension invested in FTX, while the CDPQ had $150 million in Celsius, both now bankrupt with their CEOs in prison
My upcoming book, "Bitcoin for Institutions" explains why Bitcoin is a godsend for pensions and other potential institutional use cases. It also explains why Blackrock understands Bitcoin much more than people want to give them credit for. I argue that Blackrock is looking to redefine Modern Portfolio Theory by abandoning bonds and inserting Bitcoin as the "risk-free asset" and that this is an existential solution stemming from being the primary investment manager impacted by the aforementioned Bank of England bailout. It appears now that S&P Global also understands Bitcoin. To what end is unclear to me, but I have to give credit where it is due. From their recent report titled "Cryptocurrency Is Growing Within U.S. State Reserves And Statewide Pension Plans", by credit analysts Todd Kanaster and Geoffrey Buswick, several items caught my eye and impressed me. Among them were from the summary of opportunities and risks (from the report):
Opportunities
-
Bitcoin holdings may provide a hedge against long-term debasement of fiat currency through inflation, due to bitcoin's finite supply. Its value may also be driven by geopolitical factors if its security and decentralized nature lead to its increasing adoption as a reserve asset.
-
Other crypto assets such as ether or Solana are similar to technology venture investments, as they provide exposure to upside if these technology platforms continue to see increasing adoption.
The first bullet demonstrates a clear acknowledgement that S&P understands and approves the messaging of what Bitcoin's biggest strength is. It is an astonishing acknowledgement of how debasement is a feature of fiat currency and how Bitcoin is the solution. They go as far as to explain how the decentralized nature and security carry out the solution.
The second bullet is icing on the cake, separating other crypto assets and classifying them, not as a monetary cornerstone, but as just some other potential source of return.
Risks
-
Market value risk: Historically, their prices have been volatile. They would introduce a risk factor if included in funds that are intended to cover an issuer's short-term liquidity needs (which typically do not include asset types with significant market value risk).
-
Operational and cyber: Although direct ownership of crypto requires specialized infrastructure and staffing, much of the risk is adjusted to levels comparable with those of traditional investments when held, in lieu of direct crypto ownership, in shares of a crypto ETF from a third party investment manager with robust operational practices.
-
Goal misalignment: Grouping all non-stablecoin crypto together under the same risk profile may overlook unique risk characteristics among different types of investments, such as bitcoin ownership, technology investments, or tokenized securities.
-
Regulatory uncertainty: We have seen a large swing in the regulation picture at the federal level from the new U.S administration and similar changes could happen again, either due to leadership change or even a downturn in crypto prices if that reduces investor interest.
S&P is showing a superior understanding of the risks of Bitcoin. They echo several of the risks I discuss in the book. They caution against using Bitcoin with a short-term time horizon (1st bullet), as well as admonish the idea of grouping altcoins with Bitcoin (3rd bullet). Additionally, the 2nd bullet warms my heart discussing the additional operational risk involved when trusting custody to a 3rd party, as Blackrock (and all of the Bitcoin ETF providers except for Fidelity) does. We've already seen that Coinbase uses pre-Segwit legacy addresses for the ETFs and that Blackrock is beginning to explore other options for its custodian.
It is important that pensions get this right, as it is unlikely that the Gods will be sending another lifeline. Getting this wrong will lead to a bailout that will make the Bank of England's look tame in comparison. Instead of letting the central bankers pick the winners and losers, companies and states are going to get one last chance to win on their own terms. A medium-term time horizon, and a strong understanding of what Bitcoin is and what gives it its value, is the blueprint for a road map to recovery and a series of successful, solvent plan terminations in the next 5-10 years.
-
-
 @ 2b24a1fa:17750f64
2025-04-10 19:04:23
@ 2b24a1fa:17750f64
2025-04-10 19:04:23Schon Wolfgang Borchert rief alle dazu auf, laut und deutlich „NEIN“ zu sagen, wenn der Ruf zu den Waffen ertönt. In Vorkriegszeiten, und in diesen leben wir – mal wieder –, dann ist meist nicht viel Zeit, Sand in das Getriebe der anlaufenden Kriegsmaschinerie zu werfen. Jene, die von den Kriegen profitieren, bereiten sie nicht lange vor, um kurz vorher einen Rückzieher zu machen. Die meinen das ernst! Das ist keine Übung!
https://soundcloud.com/radiomuenchen/krieg-einfach-nur-nein-von-tom-oliver-regenauer
Und deswegen formulierte neuerdings auch Tom-Oliver Regenauer ein klares und unmissverständliches „Nein“ für die „Friedenstaube“ auf der neuen, zensurresitenten Plattform Pareto. pareto.space/a/naddr1qqxnzde5xg…xarj9e3xzmny3sn3aw
Hören Sie seinen Text „Krieg? Einfach nur: Nein!“.
Sprecher: Ulrich Allroggen
Bild: Gezeichnet von Tina Ovalle
-
 @ 554ab6fe:c6cbc27e
2025-04-10 18:48:57
@ 554ab6fe:c6cbc27e
2025-04-10 18:48:57What is consciousness, and can it be changed or enhanced? This is a question that humans have struggled with for a very long time. The question of consciousness alone is daunting. Some even argue that humans will never be able to find the answer. Regardless, the quest for knowledge is not always about the answer, rather it is the journey that is revealing. This is true not only for our society, but the individual as well. The search for the truth often leads one down a path of self-reflection, and can lead to conclusions previously thought to be ludicrous. Here, I will argue that consciousness can be interpreted as an interpretation of reality, where the interpretation may become clearer and more accurate through practices such as meditation.
Consciousness
To articulate this idea, the concept of consciousness must firstly be discussed. There is an incredibly interesting TED talk given by Anil Seth, where he describes consciousness as an illusion. He explains how the brain receives signals from both the internal and external environment of the body, makes an interpretation of those signals, which creates our conscious experience. In his scientific writing, he claims that the brain can be viewed as a prediction machine1. He argues that the brain is constantly making predictions and error correcting in order to gain understanding of the signals it is receiving. He is not alone in this theory, and many other researchers concur that the constant comparison of internal predictions and external stimuli is what generates the brain’s sensations of causal forces2. There are plenty of reasons to believe this is true. Imagine, the brain is receiving all kinds of neuronal signals both from external stimuli sensors and sensors for our internal systems. These signals all shoot up the spinal cord to the brain. It is unclear that these neuronal signals are stamped with an identifier of where they came from, so the brain has to make a predictive model for not only where the signal came from, but also why the signal came at all. The latter is important for survival: the use of our senses to accurately predict our environment would be a critical reason why consciousness developed in the first place. Imagine you are an ancient hominid walking in the wild: you see a tangled cord like thing around a branch on the tree. You need to process that information, determine if it is more branch or a snake and act accordingly. This is a potential biological reason for the manifestation of thought and problem solving. This is a very meta-cognitive example of our brain receiving information and then using previous knowledge to generate a predictive conclusion on the external reality.
There are also examples of this outside of the more obvious meta-cognitive examples. A good example is the famous rubber hand experiment. The first rubber hand experiment was conducted in 1998 by Botvinick and Cohen3. In this experiment, a subject places their hand on a table with a screen blocking their view of their own hand. A rubber hand is then placed on the other side of the screen where it is visible. The experimenter rubs both the rubber hand and real hand with a paint brush. By the end of the experiment, subjects begin to feel as if the rubber hand is their own limb3. The brain, using the visual senses, detects that a hand is being stroked with a brush while sensory neurons send signals that the hand is experiencing the touch of a paint brush. These two signals cause the predicting brain to think that the rubber hand is our hand. This experiment has been repeated many times in different ways. It has been observed that participants begin to react defensively to the threat of pain or damage to the rubber hand4. This illustrates the powerful extent at which the brain processes and reacts to information that it interprets from reality. Amazingly, some research suggests that the touch aspect of the experiment isn’t even necessary to produce the illusion5. Others have recreated this experience using virtual reality, citing that when the virtual hand changed color in response to the subject’s heartbeat, a significant sense of body ownership was generated6. Body ownership, and our sense of reality is arguably determined by our brain’s interpretation of both internal and external stimuli.
The Neuroscience and Meditation
It is hypothesized that the anterior insular cortex (AIC) is involved in the comparison of the stimuli to the predicted model1. Interestingly, the same brain region is associated with the anticipation of pain7. For those unaware, there is some research to suggest that much of the pain we experience is not due to the actual noxious stimuli (physical pain sensation), but from the anticipation of that pain. Evidence for this can be found in studies such as Al-Obaidi et al. from 2005, that concluded that the pain experienced in patients with chronic low back pain could not be solely attributed to the sensor signals, but from the anticipation of the pain8. Additionally, the anticipation of pain relief is the primary contributor to placebo analgesia (placebo pain killers)9. Furthermore, a large body of research has been conducted showing that meditators show a decreased anticipatory attitude towards pain, subsequently experiencing less unpleasant pain 7,10,11. For example, chronic pain in multiple areas such as the low back, neck, shoulder, and arms have been shown to reduce after meditation practice12. Finally, an extreme case study worth noting is of a yogi master who claimed to not experience pain at all13. When this master was brought into the lab, not only did he not experience pain, but his thalamus showed no additional activation following painful stimuli13. What is fascinating about this is that the thalamus is the main relay station for all incoming somatosensory information14, and some argue that this is a candidate for the location of consciousness15. To not have strong activation here after painful stimuli is to suggest a radical change in how the brain receives incoming stimuli, and perhaps is indicative in a dramatic shift in how this individual’s conscious experiences the world. Though this is but one small example, the previous studies outline a strong case for meditation’s ability to alter the way the brain processes information. Given meditation involves the active practice of generating an open and non-judgmental attitude towards all incoming stimuli, perhaps this alters the processing of incoming stimuli, thereby changing the predictive model. On a similar note, perhaps it relates to neuroplastic changes that occur within the brain. It has been noted that the AIC is activated during times of awareness of mind wandering16. This suggests that the AIC is in use frequently during meditation practices. Perhaps it is strengthened then by meditation, thereby also allowing for greater prediction model generation. Imagine the mind as a pond. If the pond is calm and still, one single rain drop rippling in the pond is clearly identifiable. One would easily know information about the droplet, because the ripple could be easily analyzed. Now imagine a pond during a rain storm, where an uncountable amount of rain drops is hitting the pond and there are ripples everywhere. One could not adequately make out where each ripple came from, because there would be too much overlap in the ripples. This may be how the brain functions as well. When the signals are low, and no extraneous thoughts and interpretations are created from signals, then the brain’s prediction model can easily determine where and why a signal it received came from. If, however, the mind is chaotic and full of internal noise, then the brain has a harder time creating an accurate understanding of incoming stimuli and generating a correct model.
Enlightenment
Enlightenment, from a scientific point of view, has been defined as a form of awareness where a person feels that s/he has gained a new understanding of reality 17. In this sense, it bears a striking relationship to the topic of consciousness. If consciousness can be defined as our interpretation of the external and internal environment through our mental prediction model, then experiences of enlightenment are defined by moments where our interpretation is completely changed in a profound way. The experiences are often characterized by the loss of individuality and consequent identification of being part of a greater oneness 18,19. As an interesting side note, this same experience is common amongst subjects, who in a double-blinded study, take psilocybin (the active ingredient in magic mushrooms)20,21. The neuroscience of enlightenment is particularly interesting. The temporo-parietal junction of the brain is involved with self-location and body ownership22. Unsurprisingly, this area is highly involved in the illusion of the rubber hand experiment23. This is the same brain area that is hypothesized to be related to these enlightened experiences of oneness 17. If this brain area, which handles the interpretation of where and what the body is, was to decrease in activation, then the brain would generate a more ambiguous interpretation that the self and the external environment are less distinct than previously thought. This is a possible explanation to why enlightenment experiences involve a feeling of oneness with everything. To bring this all home, meditation has been shown to decrease parietal lobe activation 4,24. Suggesting that meditation can be a method of adjusting the brain’s interpretation of stimuli to generate an outlook that is unifying in perceptive.
Closing Remarks
The evidence that meditation may lead to an altered conscious living has deep philosophical implications. Meditation is a practice that, in part, involves an open awareness to all incoming stimuli alongside the absence of any meta-cognitive interpretation or processing of said stimuli. This generation of a still mind may generate a more accurate prediction model of incoming stimuli, void of any corruption on the part of our thoughts. Given the observation that meditation, both scientifically and culturally, can lead to an understanding and experience of a greater oneness amongst all suggests that this interpretation of incoming stimuli is the more accurate interpretation. It is hard to imagine that anyone would not advocate the beauty and usefulness of this perspective. If more people had this perspective, we would have a much more peaceful, happy and unified society and planet. Ironically, our culture often aims to arrive to this philosophical perspective through analytical thought. However, given the evidence in this post, perhaps it is the absence of analytical thought, and the stillness of the mind that truly grants this perspective.
**References ** 1. Seth AK. Interoceptive inference, emotion, and the embodied self. Trends in Cognitive Sciences. 2013;17(11):565-573. doi:10.1016/j.tics.2013.09.007 2. Synofzik M, Thier P, Leube DT, Schlotterbeck P, Lindner A. Misattributions of agency in schizophrenia are based on imprecise predictions about the sensory consequences of one’s actions. Brain. 2010;133(1):262-271. doi:10.1093/brain/awp291 3. Botvinick M, Cohen JD. Rubber hand ‘feels’ what eyes see. Nature. 1998;391(February):756. 4. Newberg A, Alavi A, Baime M, Pourdehnad M, Santanna J, D’Aquili E. The measurement of regional cerebral blood flow during the complex cognitive task of meditation: A preliminary SPECT study. Psychiatry Research - Neuroimaging. 2001;106(2):113-122. doi:10.1016/S0925-4927(01)00074-9 5. Ferri F, Chiarelli AM, Merla A, Gallese V, Costantini M. The body beyond the body: Expectation of a sensory event is enough to induce ownership over a fake hand. Proceedings of the Royal Society B: Biological Sciences. 2013;280(1765). doi:10.5061/dryad.8f251 6. Suzuki K, Garfinkel SN, Critchley HD, Seth AK. Multisensory integration across exteroceptive and interoceptive domains modulates self-experience in the rubber-hand illusion. Neuropsychologia. 2013;51(13):2909-2917. doi:10.1016/j.neuropsychologia.2013.08.014 7. Zeidan F, Grant JA, Brown CA, McHaffie JG, Coghill RC. Mindfulness meditation-related pain relief: Evidence for unique brain mechanisms in the regulation of pain. Neuroscience Letters. 2012;520(2):165-173. doi:10.1016/j.neulet.2012.03.082 8. Al-Obaidi SM, Beattie P, Al-Zoabi B, Al-Wekeel S. The relationship of anticipated pain and fear avoidance beliefs to outcome in patients with chronic low back pain who are not receiving workers’ compensation. Spine. 2005;30(9):1051-1057. doi:10.1097/01.brs.0000160848.94706.83 9. Benedetti F, Mayberg HS, Wager TD, Stohler CS, Zubieta JK. Neurobiological mechanisms of the placebo effect. In: Journal of Neuroscience. Vol 25. Society for Neuroscience; 2005:10390-10402. doi:10.1523/JNEUROSCI.3458-05.2005 10. Gard T, Hölzel BK, Sack AT, et al. Pain attenuation through mindfulness is associated with decreased cognitive control and increased sensory processing in the brain. Cerebral Cortex. 2012;22(11):2692-2702. doi:10.1093/cercor/bhr352 11.Grant JA, Courtemanche J, Rainville P. A non-elaborative mental stance and decoupling of executive and pain-related cortices predicts low pain sensitivity in Zen meditators. Pain. 2011;152(1):150-156. doi:10.1016/j.pain.2010.10.006 12. Kabat-Zinn J, Lipworth L, Burney R. The clinical use of mindfulness meditation for the self-regulation of chronic pain. Journal of Behavioral Medicine. 1985;8(2):163-190. doi:10.1007/BF00845519 13. Kakigi R, Nakata H, Inui K, et al. Intracerebral pain processing in a Yoga Master who claims not to feel pain during meditation. European Journal of Pain. 2005;9(5):581. doi:10.1016/j.ejpain.2004.12.006 14. Steeds CE. The anatomy and physiology of pain. Surgery. 2009;27(12):507-511. doi:10.1016/j.mpsur.2009.10.013 15. Min BK. A thalamic reticular networking model of consciousness. Theoretical Biology and Medical Modelling. 2010;7(1):1-18. doi:10.1186/1742-4682-7-10 16. Hasenkamp W, Wilson-Mendenhall CD, Duncan E, Barsalou LW. Mind wandering and attention during focused meditation: A fine-grained temporal analysis of fluctuating cognitive states. NeuroImage. 2012;59(1):750-760. doi:10.1016/j.neuroimage.2011.07.008 17. Newberg AB, Waldman MR. A neurotheological approach to spiritual awakening. International Journal of Transpersonal Studies. 2019;37(2):119-130. doi:10.24972/ijts.2018.37.2.119 18. Johnstone B, Cohen D, Konopacki K, Ghan C. Selflessness as a Foundation of Spiritual Transcendence: Perspectives From the Neurosciences and Religious Studies. International Journal for the Psychology of Religion. 2016;26(4):287-303. doi:10.1080/10508619.2015.1118328 19. Yaden DB, Haidt J, Hood RW, Vago DR, Newberg AB. The varieties of self-transcendent experience. Review of General Psychology. 2017;21(2):143-160. doi:10.1037/gpr0000102 20. Griffiths RR, Richards WA, McCann U, Jesse R. Psilocybin can occasion mystical-type experiences having substantial and sustained personal meaning and spiritual significance. Psychopharmacology. 2006;187(3):268-283. doi:10.1007/s00213-006-0457-5 21. Griffiths RR, Richards WA, Johnson MW, McCann UD, Jesse R. Mystical-type experiences occasioned by psilocybin mediate the attribution of personal meaning and spiritual significance 14 months later. Journal of Psychopharmacology. 2008;22(6):621-632. doi:10.1177/0269881108094300 22. Serino A, Alsmith A, Costantini M, Mandrigin A, Tajadura-Jimenez A, Lopez C. Bodily ownership and self-location: Components of bodily self-consciousness. Consciousness and Cognition. 2013;22(4):1239-1252. doi:10.1016/j.concog.2013.08.013 23. Tsakiris M, Costantini M, Haggard P. The role of the right temporo-parietal junction in maintaining a coherent sense of one’s body. Neuropsychologia. 2008;46(12):3014-3018. doi:10.1016/j.neuropsychologia.2008.06.004 24. Herzog H, Leie VR, Kuweit T, Rota E, Ludwig K. Biological Psychology/Pharmacopsychology. Published online 1990:182-187.
-
 @ 88cc134b:5ae99079
2025-04-10 16:02:49
@ 88cc134b:5ae99079
2025-04-10 16:02:49sasas sasa sasa
-
 @ 88cc134b:5ae99079
2025-04-10 15:57:14
@ 88cc134b:5ae99079
2025-04-10 15:57:14article
-
 @ f1989a96:bcaaf2c1
2025-04-10 14:25:09
@ f1989a96:bcaaf2c1
2025-04-10 14:25:09Good morning, readers!
Today, HRF takes part in the launch of the Bitcoin Humanitarian Alliance in London, where a dozen human rights and aid groups will convene with policymakers, media, finance professionals, and technologists at the Frontline Club to explain how they are using Bitcoin in their work in the field.
Elsewhere, we bring news from Turkey, where large, pro-democracy protests erupted over President Recep Tayyip Erdogan’s increasing political repression and economic fallout. The Turkish regime has detained more than 2,000 protesters (and counting) as youth appear in droves demanding democracy, accountability, and economic reform.
In Eastern Africa, Tanzania’s government extended immense restrictions on foreign currency, effectively barring its use in day-to-day payments outside a few circumstances. In a poverty-stricken country where fuel prices have moved forcibly upward for two consecutive months, access to and usage of alternative currencies can be a financial lifeline.
In Bitcoin news, we spotlight Misty Breez, a new open-source Bitcoin wallet built by Lightning Network infrastructure company Breez. The wallet is a Lightning and Liquid Network hybrid wallet. It gives users control over their funds and abstracts away any complexities of payment channel management, but users must trust the Liquid Federation. In terms of functionality, Misty Breez supports a wide variety of address types, offering users flexibility across the fees, privacy, and censorship resistance of their payments. It may prove a helpful tool for dissidents and activists standing against tyranny.
We end with the latest edition of the HRF x Pubkey Freedom Tech Series, where HRF’s Ayelen Osorio joins Zimbabwean pastor-turned-activist Evan Mawarire, who recounts his inspiring journey of a peaceful uprising against Robert Mugabe’s dictatorship and the hyperinflation and repression he unleashed on the population. We also feature the live streams of the 2025 MIT Bitcoin Expo in collaboration with HRF. These videos highlight the speakers, panels, and activities led by HRF to raise awareness about financial repression and the tools being built to resist it.
Now, let’s jump right in!
SUBSCRIBE HERE
GLOBAL NEWS
Turkey | Government Detains Thousands of Pro-Democracy Protesters
The largest protests in over a decade erupted in Istanbul, Turkey, after President Recep Tayyip Erdoğan detained political opposition figure and Istanbul Mayor Ekrem Imamoglu. Turks of all walks of life find themselves united by common outrage at the regime’s ongoing political repression and tumultuous economic conditions. With inflation soaring above 39% and widespread unemployment among the nation’s youth, it’s no surprise Turks are flooding the streets and demanding change. In response to these demonstrations, law enforcement has since detained more than 2,000 demonstrators, and police blockades have met student protesters with water cannon trucks to suppress their dissent. Many young Turks feel their future is slipping away in a country where saving is futile, the currency is collapsing, and speaking out comes at a high personal cost. “This feels like our last chance,” one young protester said, adding, “If we don’t succeed, many of us will have to leave Turkey.”
Tanzania | Regime Enacts Restrictions on Foreign Currency
Tanzania’s regime is banning the use of foreign currency outside of a few circumstances (such as duty-free retailers and government membership fees). This means quoting prices in, accepting, or facilitating payments with foreign currency is now illegal, alongside declining to accept the official Tanzanian shilling (TZS). Losing the ability to transact with more stable currencies removes individuals’ ability to shield themselves from inflation and subjects them to local currency volatility. The mandate comes in addition to the Energy and Water Utilities Regulatory Authority raising the cost of fuel for a second consecutive month. Locals worry this could further increase the cost of living as the fuel price hike ripples through the economy. These policies mirror the tactics of authoritarians using financial control to limit dissent and restrict individual financial freedom.
China | Incorporates e-CNY CBDC into Financial Sector Guidelines
China is incorporating the e-CNY central bank digital currency (CBDC) into financial sector guidelines for the first time, signaling a strengthening commitment to fully roll out its CBDC. The e-CNY’s usage is reportedly expanding among Chinese citizens, with the Chinese Communist Party (CCP) claiming 800 million wallets and over 10.2 trillion CNY in transaction volume — though these numbers are both dubiously high and difficult to independently verify. As usage grows, so do concerns over financial and individual liberties. The CCP already uses the financial system to monitor and suppress dissent. For Uyghurs, a Muslim minority in the Uyghur Region grappling with ongoing cultural genocide, mass surveillance, and forced labor from the CCP, the e-CNY would allow the regime to restrict their financial autonomy and freedom completely. As it begins to roll out, it’s important to become aware of the dangers of the e-CNY here.
Burkina Faso | Arrests Three Journalists in Press Crackdown
Burkina Faso’s military junta arrested three journalists for reporting on regime-imposed press restrictions. Since seizing power in 2022, the military junta, under the leadership of Ibrahim Traoré, has targeted independent media by detaining reporters, forcing critics into exile, abusing emergency laws to suppress dissent, and using financial repression to disrupt independent funding. Journalists disappear under the guise of forced conscription, international coverage of military abuses is blocked, and outlets that report on crimes against humanity are eradicated. With press freedom in ashes, Burkinabés face an information blackout where state propaganda proliferates. In these contexts, open and uncensorable protocols like nostr can serve as a digital town square where information, value, and assembly flow undisturbed by the reach of oppressive regimes.
Tunisia | Saied Sacks Prime Minister as Economy Crumbles
Tunisian President Kais Saied dismissed Prime Minister Kamel Maddouri less than a year into his term and replaced him with Sara Zaafarani, Tunisia’s third prime minister in under two years. As Saied reshuffles his cabinet to best suit his interests and goals, Tunisia’s economy has reached a standstill. Growth is running below 1.5%, the cost of living continues to climb, and shortages of staple goods like rice, sugar, and coffee burden the everyday lives of Tunisians. After staging a coup, dissolving the government, and ruling by decree, Saied’s consolidation of power has come inch by inch with the erosion of democracy and financial stability.
BITCOIN AND FREEDOM TECH NEWS
Breez | Releases New Open-Source Bitcoin Wallet
Breez, a company helping build out the Bitcoin Lightning economy, released a new open-source Bitcoin wallet called “Misty Breez.” It is a hybrid Lightning and Liquid Network wallet built using the Nodeless Breez SDK. The wallet offers fast and private transactions without the complexities of payment channel management. The tradeoff? Trusting the Liquid Federation with custody of your Bitcoin. Still, Misty Breez supports many Bitcoin and Lightning features, including on-chain payments, Lightning addresses, BOLT 12 invoices, and offline receiving. So, while the wallet is a trust-minimized solution rather than fully custodial, users gain a wide range of use cases and features unique to this wallet. This could make Misty Breez useful for people facing financial surveillance, internet outages, or authoritarian-imposed financial restrictions. Learn more about the wallet here.
OpenCash | Bounty for Open Source Cashu x BTCPay Server Plugin
The OpenCash Association is offering a two million satoshi bounty for an open-source plugin allowing merchants to accept Cashu payments through BTCPay Server. Cashu is a Bitcoin-based ecash protocol designed to offer fast, low-cost, and very private transactions. For activists and dissidents, ecash enables payments without compromising financial privacy, but they must trust the mints (entities managing the system) to custody their funds. OpenCash specified that the Cashu plugin must integrate cleanly with BTCPay Server and include an input field for ecash redemption or a scannable Cashu payment request. If claimed, this bounty and subsequent integration will help advance Bitcoin’s medium of exchange capabilities and make private payments more accessible by integrating with self-hosted, independent Bitcoin payment infrastructure. Learn more about the bounty here.
Machankura | Adds Support for Offline Bitcoin Transactions in Uganda
Machankura, a custodial Bitcoin Lightning wallet that helps Africans access Bitcoin without the Internet, announced they expanded service to Uganda, enabling Ugandans to use Bitcoin without an Internet connection. To do so, Machankura leverages the Unstructured Supplementary Service Data (USSD) protocol for sending text messages. To use the service, users simply dial a designated number on a feature phone (or a smartphone without data) and can access the Bitcoin network in countries like Nigeria, Malawi, Zambia, and now Uganda. Machankura helps democratize Bitcoin access, expands censorship-resistant money across Africa, and offers a practical solution to financial inclusion. If you’re in Uganda or another supported country, try it here.
Zeus Wallet | Plans to Introduce Cashu Support
Zeus, a leading self-custodial mobile Lightning wallet, shared plans for a future Cashu integration. Cashu is an ecash protocol for Bitcoin. It enables practical everyday payments on Bitcoin that are private by design (but users must trust mints to manage their funds). By adding ecash support, Zeus can expand the accessibility of private Bitcoin payments and provide its users with greater flexibility over their financial activity. As part of its upcoming release, the wallet also introduces two new types of addresses: Zaplocker addresses for Lightning self-custody on mobile and Nostr Wallet Connect (NWC) addresses for remote node runners. While a little more technical, these integrations will improve individuals' ability to transact without exposing their financial history, reducing surveillance risks, especially for those living under authoritarian regimes or in jurisdictions with strict financial controls.
Bitcoin Thailand Festival | Half-Marathon to Challenge Financial Repression
The Thai city of Chiang Mai will host the nation’s inaugural Bitcoin Half Marathon and Bitcoin Thailand Festival from Nov. 1-2, 2025, under the theme “Run For Freedom.” The marathon’s theme contrasts Thailand’s increasing financial repression and long history of erasing dissent. Even still, the festival’s mission to advance financial freedom and financial literacy with participation from the local Bitcoin community comes at a pressing time. The Thai government is increasingly restricting financial freedoms through digital cash handouts, which, for all intents and purposes, function as a central bank digital currency that imposes spending restrictions and expiration dates on money. In these environments, Bitcoin education and awareness are more urgent than ever.
Btrust Builders | Announces Builders Pathways
Btrust Builders introduced Btrust Builders Pathways, a new program designed to equip African developers with the skills and experience needed to contribute to Bitcoin open-source software. The initiative offers five learning tracks, from beginner-friendly Bitcoin fundamentals to advanced Rust programming and Bitcoin Core development. Participants will gain hands-on experience, mentorship, and access to potential funding via Btrust Developer Grants. With this launch, Btrust Builders continues its mission to grow Africa’s Bitcoin development talent and strengthen the software’s ecosystem in a region where many suffer under dozens of authoritarian governments.
RECOMMENDED CONTENT
How Bitcoin Fights Corruption & Injustice with Evan Mawarire
In the latest edition of the HRF x Pubkey Freedom Tech Series, HRF’s Content & Research lead Ayelen Osorio sits down with Zimbabwean pastor-turned-activist Evan Mawarire to explore how Bitcoin can serve as a tool for fighting inflation, corruption, and injustice. Together, they unpack Mawarire’s personal journey of leading a peaceful uprising against the tyranny of Robert Mugabe and the hyperinflation he unleashed on his undeserving population. Mawarire details how Zimbabwe’s economic collapse became an orchestrated strategy to control and silence Zimbabweans. He further explains how the peaceful movement galvanized a generation, why financial repression is a central pillar of authoritarianism, and how Bitcoin offers ordinary citizens a way to resist and rebuild. Catch the full conversation here.
MIT Bitcoin Expo Livestream
Last week, software developers, human rights activists, students, and researchers gathered at the Massachusetts Institute of Technology (MIT) for the 12th annual MIT Bitcoin Expo — this year in partnership with HRF — to explore how Bitcoin and freedom technologies can defend civil liberties and empower individuals, especially under authoritarian regimes. Born from MIT’s 2014 Bitcoin Project, the expo has grown into a major forum for individual liberation, with panels, workshops, and hackathons centered on privacy, financial autonomy, and decentralized protocols. Tune into the livestream recording to catch the speakers, presentations, and panels that defined the event.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ fbf0e434:e1be6a39
2025-04-10 14:13:23
@ fbf0e434:e1be6a39
2025-04-10 14:13:23Hackathon 概要
由 Flare 与 Google Cloud 合作举办的 Flare x Google Verifiable AI 线上黑客松&线下黑客松 于 2025 年 3 月同期举行,聚焦可验证自主 AI 应用开发,推动区块链与人工智能技术的深度融合。提交项目涵盖 Social AI Agent、RAG Knowledge、AI x DeFi(DeFAI)和 Consensus Learning 四大核心类别。依托 Google Cloud 机密计算与 Flare 预言机技术,为数据密集型 AI 应用提供安全可信的链上链下协同支持,同时通过线上辅导、技术研讨会及与伯克利大学、DoraHacks 等机构合作,助力开发者实现技术落地
所有获奖者由 Flare 联合创始人 Hugo Philion、Google Cloud 代表 Ross Nicoll 等行业专家组成的评审团评定。线上黑客松于 3 月 7 日至 14 日开展,总奖池 40,000 美元,吸引了 358 名开发者参与,最终提交审核通过了 46 个的创新项目。线下黑客松于 3 月 7 日至 9 日在加州伯克利大学举办,总奖池 60,000 美元,共有 105 位开发者现场参与,提交了 24 个项目。
此次黑客松通过技术整合验证了 AI 代理在去中心化场景中的可信运行机制,为 DeFAI、隐私计算等领域提供实践案例,同时构建产学研一体化平台,加速区块链与 AI 技术的跨领域应用,标志着两大技术在去中心化生态中的深度协同进入新阶段。
线上黑客松获奖者
Social AI Agent 奖项获得者
-
ScribeChain - 该项目利用AI将X Spaces中的实时音频转换为简明的文字摘要,帮助有效的信息处理。
-
Gosenica je lezla - Telegram 机器人,使用 RAG 数据库分离代码/文档,用于 Flare 文档查询和代码示例生成。
-
Flarebot - Flare 的 AI 驱动 Telegram 机器人,提供 DeFi 分析,通过 FTSOv2 和 Gemini 模型进行代币价格/TVL 跟踪。
RAG Knowledge 奖项获得者
-
Decentralized Trusted AI - 引入去中心化区块链系统以验证 AI 生成的响应,从而增强对 AI 输出的信任。
-
chaincontext - 可验证知识系统,将 FTSO 数据、区块链状态和 RAG 合并在 TEE 中,以进行透明的信任评估。
AI x DeFi (DeFAI) 奖项获得者
-
Quince Finance - 该项目结合了由 AI 驱动的聊天机器人和 Google Cloud 于 Flare 上的 DeFi 网页应用中,专注于提高用户安全和访问。
-
Flare DeFAI - 在 TEE 中提供安全的 AI 助手,使用自然语言进行 DeFi 操作并在 Flare 上进行智能合约风险评估。
-
Flare Sense - 使用实时监控、RAG 和 Telegram 警报检测风险并建议解决方案的 DeFi 安全代理。
Consensus Learning 奖项获得者
-
DemistiFI - 在自动钱包管理中利用 AI 代理,并采用共识学习来实现一致、可靠的交易。
-
Flava AI - 构想 Flare 网络与爬虫、分块器和嵌入器组件进行交互的智能 RAG 和共识机制。
-
Forecaster - 多模型共识平台,通过信心评分和技术分析提高市场预测,以便更好地进行投资决策。
有关这些项目的更多信息,请访问 DoraHacks。
线下黑客松获奖者
Social AI Agent 奖项获奖者
1st Place:
- Flare Fact Checker - 开发了一种基于 AI 的事实检查工具,利用可信执行环境中的验证节点验证社交媒体上的科学声明。
2nd Place:
- FlareBot - 一个 Discord 机器人,为 Flare 社区提供 24/7 支持,具有实时数据检索和可定制的安全过滤器。
3rd Place:
- Flara - 为开发者关系自动化社交媒体互动提供 AI 代理,结合 Gemini-2.0-Pro 模型和可信执行环境确保自主性验证。
RAG Knowledge 奖项获奖者
1st Place:
- Command Flare - 为 DeFi 提供自然语言 AI 界面,使用新颖的图形和向量方法在安全环境中增强交易和查询。
2nd Place:
- 2DeFi - 通过为传统金融用户提供个性化投资策略和 AI 分析,简化在 Flare 区块链上的 DeFi 访问。
3rd Place:
- ragstoriches - 提供抓取、解析和组织区块链数据的工具,以提高分析和响应准确性。
AI x DeFi (DeFAI) 奖项获奖者
1st Place:
- 2DeFi (同时获得 RAG Knowledge 类别的奖项)
2nd Place:
- Voice To Flare - 促进在 Flare 区块链上的安全、多语言区块链交易,借助 AI 增强。
3rd Place:
- Solar v1 - 一个 AI 驱动的 DeFi 助手,通过高级分析和自动化增强在 Flare Network 上的互动。
Consensus Learning 奖项获奖者
1st Place:
- NFT Deep Appraisal - 使用共识学习结合 AI 评估 NFT 价值,结合数据分析和一致性验证。
2nd Place:
- mikey-codebase - 实施了一种合奏 LLM 响应聚合器,包括评估模型影响的 Shapley 估计。
3rd Place:
- Command Flare (也在 RAG Knowledge 类别中获得名次)
欲了解完整的项目列表和更多信息,请访问 DoraHacks。
关于组织者
Flare
Flare 是一家专注于推动区块链解决方案和智能合约应用的技术组织。Flare 以将以太坊虚拟机集成到更广泛的区块链生态系统中而闻名,实现跨链互操作性。Flare Network 是该公司的一个著名开发项目,通过促进各种网络之间的无缝交易,增强数字资产的实用性。Flare 继续扩展去中心化技术能力,推动创新和更广泛的区块链采用。
-
-
 @ fbf0e434:e1be6a39
2025-04-10 14:00:14
@ fbf0e434:e1be6a39
2025-04-10 14:00:14Hackathon 概要
HackSecret 5 展示了在去中心化机密计算中的创新,共吸引了 142 位开发者参与并提交了 53 个项目。此 Hackathon 利用 Secret Network 的特性推进了在 Cosmos、EVM 和 Solana 等区块链平台上的机密 AI 应用。
参与者探索了四个主要方向:Secret AI 应用、Autonomys Network dApps、跨链 dApps 和原生 Secret Network dApps。值得注意的项目包括利用 Secret AI SDK 的 AI 驱动法律助理和私密健康咨询平台。
此次 Hackathon 亮点在于通过 Secret Network 增强安全通信和存储的应用。例如,一个去中心化的 AI 人才市场和机密 AI 写作助手,都关注于去中心化应用中的隐私和数据机密性。
总奖池为 15,000 美元,表彰了项目的技术复杂性、创新性和可能的实际应用。HackSecret 5 促进了跨领域合作并激发了对去中心化应用的兴趣。
Hackathon 获奖者
Secret AI dApps 奖项获奖者
此类别表彰了创新利用 Secret Network 的 Secret AI SDK 的 dApps。
- Sentinex: 一个通过 AI 驱动的合约审计和机密分析增强 DeFi 安全的多代理平台,利用 Secret SDK 和 Autonomys 代理进行安全的代币推出和智能合约审计。
- Secret AI Accountant System: 通过结合 Confidential Computing 和 Secret Network 的 AI 安全管理商业账簿,以实现透明的审计过程。
- JS SDK for Secret AI: 通过简单的 JavaScript API 轻松将 Secret Confidential AI 模型集成到 Web 应用中。
- Conflux-AI: 一个去中心化平台,通过联合学习和智能合约实现隐私感知的协同交易及全球模型聚合。
- DocAssist: 通过 AI 洞察安全管理患者数据,利用 Secret AI SDK 支持医生。
- codeforgeai: 促进 AI 与区块链的协作编码开发工具生态系统,提供像 CodeForge CLI 这样的工具。
- Secret AI Writer: 一个确保内容隐私的 AI 写作平台,通过 Secret Network 的智能合约和端到端加密实现。
- autonomous-copilot: 结合 AI 和去中心化存储的安全数据分析数据管理工具。
- SecureChat AI: 提供 AI 驱动的加密聊天,确保跨设备的安全通信。
Native Secret dApps 奖项获奖者
此类别强调了构建于 Secret Network 上的 dApps,注重默认隐私机制。
- Unchained Poker: 一个使用秘密合约解决信任问题的去中心化扑克平台,提供统计分析和语音聊天以增强安全性。
- HabiChain: 部署区块链用于安全的心理健康支持,利用功能行为分析提供个性化工具,同时保护隐私。
使用 Autonomys Agents Framework 的不可阻挡 AI 代理奖项获奖者
此类别表彰了使用 Autonomys Agents Framework 开发具有可验证链上记忆 AI 代理的项目。
- AgentMint.AI: 自动化跨区块链的 AI 驱动 meme 币创建和管理,集成社交媒体工具。
- Aetherlink: 实现 ai3:// 协议以标准化内容访问和发现于去中心化网络中。
- Pixel Lock: 使用 Auto Drive 提供安全图像存储解决方案,保护数据隐私,消除未经授权访问风险。
- Conflux-AI
Autonomys Track 2: 使用 Auto Drive 构建 - 永久去中心化存储奖项获奖者
此方向寻求利用 Auto Drive 的数据持久性和安全性解决方案,超越传统的固定方法。
- autonomous-copilot
- Decentralized Collaborative File Repository (DCFR): 基于 DAO 的文件管理,通过去中心化存储和治理协议提供民主控制和透明操作。
有关所有 hackathon 项目的更多信息,请访问 HackSecret 5 Projects。
关于组织者
Secret Network
Secret Network 是一个通过 Intel SGX 技术、加密和密钥管理实现隐私功能的区块链平台。它支持可扩展的、无需许可的智能合约,默认设计了隐私功能,支持独特的区块链应用。Secret Network 于 2020 年 9 月在其主网上推出了私密智能合约,确立了其在隐私导向区块链开发中的角色。该组织持续探索隐私在区块链技术中的创新应用。
-
 @ 7e538978:a5987ab6
2025-04-10 13:14:04
@ 7e538978:a5987ab6
2025-04-10 13:14:04After five years and over 6,000 commits, LNbits has reached a momentous milestone: Version 1.0.0 is here. LNbits is officially out of beta!
This release represents the five years relentless development, dedication, bug-hunting, feature-building, and community involvement. What started as a lightweight Lightning wallet application for Lightning Network payments has evolved into one of the most versatile, modular, and widely-used Bitcoin tools in the space.
We want to offer a heartfelt thank you to every contributor, developer, tester, and user—from those running LNbits for personal use to the communities and businesses who rely on it every day. Your feedback, bug reports, feature requests, and support have made LNbits what it is today.
🚀 Key Highlights in v1.0.0
- LNbits now at v1.0.0 – the software is stable, hardened, and production-ready.
- Vue 3 migration – a complete frontend overhaul for performance and long-term maintainability.
- WebSocket payments – faster and more efficient, replacing older SSE and long-polling methods.
- New lnbits.sh install script – simplifies setup and local deployment.
- Access Control Lists (ACL) – token-based permissions for powerful role and scope control.
- Admin tools:
- Admin payments overview
- Toggle outgoing payments
- View payments from deleted wallets
- NWC (Nostr Wallet Connect) support
- Login with Nostr or OAuth – expanding integration and authentication options
💱 Fiat & Exchange Upgrades
- Custom exchange providers
- Improved fiat precision
- Wallet-level fiat tracking and labels
- Support for Bitpay and Yadio fiat rate providers
🧑🎨 UI / UX Improvements New Login/Register interface
- Default theme for new users
- Custom background images
- Visual refresh with new themes (including neon and light/dark modes)
- Revamped Pay Invoice dialog and invoice creation
- Custom wallet icons/colours
- CSV export and in-wallet payment filtering
🛠️ Developer Tools & Internal Enhancements Migration to pyjwt, updated to breez-sdk 0.6.6, pyln-client 24.5
- Support for Python 3.10–3.13
- New nodemanager for managing Lightning channels
- Backend refactors, improved database handling, type hinting, and extension logic
- More robust testing and CI support
🩹 Maintenance & Fixes Persistent fix for admin removal bug
- Improved extension handling
- Bug fixes across wallet logic, funding sources, and legacy compatibility
- Dozens of improvements to reliability, performance, and developer experience
🎉 A Huge Thank You
To every developer, translator, tester, UX contributor, node runner, and user: thank you.
LNbits wouldn’t be what it is without your involvement. Whether you've written code, opened issues, translated labels, or simply used it and given feedback—this release is yours too.
Here's to the next chapter!
-
 @ 7d33ba57:1b82db35
2025-04-10 11:09:40
@ 7d33ba57:1b82db35
2025-04-10 11:09:40Tucked into Italy’s far northeastern corner, Trieste feels like a place where cultures meet and stories linger. With Austro-Hungarian architecture, Adriatic views, literary cafés, and a unique Central European flair, it’s Italy—but not quite like the Italy you know. Bordering Slovenia and once the seaport of an empire, Trieste is full of quiet charm and timeless elegance.
🌟 Top Things to Do in Trieste
1️⃣ Piazza Unità d’Italia
- One of Europe’s largest sea-facing squares
- Surrounded by grand buildings and open to the Adriatic—sunsets here are magical
- Great spot to sit at a café and people-watch
2️⃣ Castello di Miramare
- A fairy-tale white castle perched over the sea, built for Archduke Ferdinand Maximilian
- Explore the ornate interiors and stroll the surrounding park with sea views
- A short bus or bike ride from the city
3️⃣ Canal Grande & Borgo Teresiano
- A small Venetian-style canal lined with cafés, bridges, and boats
- At its end, you’ll find the neoclassical Sant’Antonio Nuovo church
- The area is perfect for evening walks and aperitivo
4️⃣ Caffè Culture & James Joyce Trail ☕📖
- Trieste has a legendary café scene—literary, elegant, and historic
- Visit Caffè San Marco or Caffè degli Specchi
- Follow the trail of James Joyce, who lived here for over a decade
5️⃣ Barcola Promenade
- A local favorite for seafront walks, swimming, and sunbathing
- Bring a towel, grab a gelato, and relax like a true Triestino
- Especially lively in summer
🏛️ Also Worth a Visit
- Teatro Romano – A well-preserved Roman theater right in the city center
- Castello di San Giusto & Cathedral – Hilltop views and Roman ruins nearby
- Risiera di San Sabba – A sobering WWII concentration camp memorial site
🍝 What to Eat in Trieste
- Jota – A hearty stew of sauerkraut, beans, and potatoes (Slavic roots!)
- Seafood everything – Fresh Adriatic catch, especially scampi and sardoni
- Strudel, goulash, and schnitzel – Trieste’s menu mixes Italian and Mitteleuropean
- Pair with local wines like Vitovska or a crisp Malvasia
🎯 Tips for Travelers
✅ Trieste is walkable and elegant—bring comfy shoes for those marble pavements
✅ Great base for day trips to Miramare Castle, Grotta Gigante, or even Ljubljana and Piran
✅ Try the osmize in the surrounding hills—rustic, family-run wine farms that open to the public
✅ Slovenian and Croatian borders are right nearby—Trieste is a crossroads city -
 @ a0c34d34:fef39af1
2025-04-10 09:13:12
@ a0c34d34:fef39af1
2025-04-10 09:13:12Let’s talk longevity and quality of life. Have you prepared for Passover or Easter? Do you celebrate either? I’m going to my niece’s house for Passover and I will be devouring brisket and strawberry shortcake. I use to love the Easter candy my neighbor shared when I was a kid. Taboo during Passover but I snuck a peep or two. How afraid are you about the future? Are you keeping up with longevity technology? Do you have the dream of living a long, long life? Longevity technology combines the power of medicine, biotechnology and artificial intelligence to extend a healthy human lifespan. It’s about using cutting edge technology and medical advancements to extend the years we live in good health. The focus is on quality of life during extended years. With the rise of AI powered longevity clinics, treatments tailored to an individual’s genetic profile, lifestyle and medical history, and customized anti-aging interventions, personalized healthcare will become a reality over the next decade. I’m scared I won’t be able to afford housing or healthcare. Advanced medical services cost money, and they are only going to rise. As we stay independent longer and capable of living on our own, there will be more “smart” solutions available, more longevity technology advances. Imagine using the technology of today to have a home where you feel safe for your mother or grandmother so they can live independently. The costs of technology for a “smart” house? Running lights on the floorboards light up as you walk by, just one item I can think of that can keep senior citizens safe at home. I developed a plan for a 55+ community for senior citizens. I have seen similar plans. I think blockchain technology and utilizing tokenomics can only make housing cost effective for senior citizens in the future. When I sat down and wrote the Executive Summary for Onboard60 three years ago, a component was to develop a 55+ Active Senior Community using tokenomics, smart contracts and blockchain technology. Since then, when I say I want to make Onboard60 like the AARP of today, I’ve been told that’s impossible, not going to work and I am wasting my time with this whole project, senior citizens aren’t interested. They will be. As we move into a population explosion of senior citizens living longer, healthy and independently, I think we need to consider how we are going to afford our longevity. What type of care will you receive, how much will it cost? What will you be able to control as in the cost, the level of care you receive. What currency is used? Yes, currency. As we move forward with the integration of cryptocurrency into our financial system, we need to think of what currency is accepted. There will be facilities that use their own stablecoin or accept certain others. The non-traditional financial systems are here to stay. The United States has incorporated a few different cryptocurrencies. Large financial institutions have adapted to putting cryptocurrency into their investment portfolios. I didn’t expect this to happen in my lifetime. Seriously, I thought Onboard60 would have a few more years to develop, create a community of senior citizens. That’s not the case. The world is accelerating at an impossible rate to keep up with everything. It can be overwhelming and scary. How do I find companies that use blockchain and smart contracts? Are there companies where I can protect my property rights by putting them on chain? Are there health insurance companies that use smart contracts? Onboard60 is more than the Metaverse, YouTube and A Handbook for Noobies (Web3 1101 for Seniors). It’s about staying informed, safely, to achieve the future every senior citizen deserves. If you have any knowledge of such companies, please let me know. I have crypto accountants and lawyers in my toolbox. I look forward to adding to my toolbox. I want to be like the AARP for today’s world.
Thanks for reading, Be fabulous, Sandra Abrams Founder Onboard60
-
 @ 4fe14ef2:f51992ec
2025-04-10 09:01:02
@ 4fe14ef2:f51992ec
2025-04-10 09:01:02Hey Bitcoiners,
Leave a comment below to share your hustles and wins. Let us know what you've sold this week. Have you sold it for #sats or #zaps? It doesn't matter how big or small your item is, solid or #digital, product or #service.
Just share below what you’ve listed, swapped, and sold. Let everyone rave on your latest #deals!
New to ~AGORA? Dive into the #marketplace and turn your dusty gears into shiny #BTC!
originally posted at https://stacker.news/items/939612
-
 @ 20986fb8:cdac21b3
2025-04-10 08:59:38
@ 20986fb8:cdac21b3
2025-04-10 08:59:38社交应用正迎来全新阶段:从传统的中心化平台迈向去中心化生态,用户对轻量级、智能化和隐私保护的应用需求与日俱增。在这一趋势下,Mini Apps 凭借其快速开发、灵活部署和去中心化的特性,正在成为社交应用的主流选择。加密货币支付的兴起进一步推动了这一趋势,其低成本、无国界和金融自由的优势,不仅大幅降低了交易门槛,还为 Mini Apps 的规模化发展注入了强劲动力。作为比特币生态 Nostr 协议上最受欢迎的去中心化社交支付客户端之一,YakiHonne 凭借卓越的用户体验和便捷的社交支付功能,覆盖全球 170 多个国家。如今,YakiHonne 即将推出可编程 Smart Widgets——一款支持 Mini Apps 的开发者组件。这款产品将重新定义用户在社交平台上的互动与消费方式,为链上应用生态和社交支付带来全新活力。
YakiHonne Smart Widgets:社交与消费的创新引擎
YakiHonne Smart Widgets 是一款融入社交动态的可编程微型应用,让用户在浏览内容时就能轻松完成链上支付、互动和操作。它不仅是一款工具,更是一个开放的去中心化应用市场,为用户和开发者带来无限创造力与灵活性。
Smart Widgets 提供三种简单易用的创建方式,满足不同用户的需求:
- 基础组件(Basic Widgets):任何用户都能通过直观编辑器快速创建,只需选择模板、输入内容,就能生成打赏、Mint 或投票等互动功能。用户在浏览动态时,点击按钮即可完成链上操作,体验快速、无需跳转。
- 动作组件(ActionWidgets):用户可通过嵌入应用链接快速创建,无需开发经验。普通用户点击动态中的按钮,就能直接在当前界面访问外部去中心化应用(如交易所),享受顺畅不中断的体验。
- 工具组件(Tool Widgets-Mini App):适合有开发能力的用户或开发者,通过 Smart Widgets SDK 打造功能更丰富的应用,支持复杂链上操作。用户在社交动态中即可完成数据查询、链上任务、游戏互动或即时支付,体验高度集成且流畅。
主要特性:
- 快速构建:开发者仅需数小时即可将创意变为现实,支持常用 Web 技术,打造接近原生应用的体验,无需繁琐的应用商店审核。
- 社交登录:用户无需账号密码即可进入 Mini Apps,直接使用 Nostr/YakiHonne 身份在动态中互动,流程简单,社交体验更紧密。
- 易于发现与留存:通过动态 feeds 一键发现新应用,内置裂变机制助力快速传播,Mini App 商店提供更多选择,用户可保存喜爱应用并通过通知随时回归。
- 即时互动与消费:Mini Apps 通过 YakiHonne 的社交支付功能基础设施实现无缝集成,用户无需离开动态即可完成支付、投票或游戏等操作。社交互动与链上行为自然融合,消费体验轻松融入每一次互动场景。
改变日常体验:Smart Widgets 的多场景应用
YakiHonne Smart Widgets 将社交互动与链上消费深度结合,为用户带来多样化的应用场景:
- 链上互动:用户在浏览动态时,可通过 Smart Widgets 参与链上投票或轻量游戏。例如,一键完成社区提案投票,或与好友挑战链上小游戏,互动即刻完成,无需跳转。
- 智能 Agent:用户可使用 Agent Widgets 自动创作并发布内容,例如生成个性化帖子或短视频,打造 AI 驱动的新型媒体体验。
- DAO 治理:基于aMACI创建匿名投票,结合 Agent 实现自主治理。用户直接在社交动态中参与 DAO 决策,推动去中心化社区发展。
- 社交支付:用户可通过动态发送即时支付或链上红包,例如分享一笔小额打赏,激发好友互动与消费转化。
- 订阅服务:支持内容创作者或应用的连续订阅,用户一键订阅喜爱的服务,享受无缝续费体验。
这些场景不仅提升了用户的参与感和便利性,还为创作者、开发者及社区提供了新的增长机会。
引领新趋势:Smart Widgets 的生态价值
YakiHonne Smart Widgets 的推出将为链上消费应用生态和社交支付带来深远影响。它为开发者提供了一个开放的舞台,任何人都可以通过 Widgets 快速部署创新应用,丰富 YakiHonne 的生态多样性。YakiHonne 的社交支付功能基础设施进一步为 Mini Apps 赋能,提供高效的支付支持,降低了开发者的支付集成成本,同时为用户带来安全、便捷的交易体验。这种支持不仅加速了 Mini Apps 的商业化进程,还推动了链上消费的规模化增长。
对于用户而言,Smart Widgets 将社交互动与消费行为融为一体,创造更具沉浸感和实用性的数字体验。对于内容创作者和社区,它则提供了一个低门槛的链上入口,助力其触达全球用户。这一产品不仅是对技术边界的探索,更是对未来去中心化生活方式的预演。YakiHonne 致力于通过 Smart Widgets 构建一个开放、活跃的社交与消费生态,让每一次互动都成为链上价值流动的起点。
立即体验:Smart Widgets 等你探索
YakiHonne 诚邀全球用户和开发者共同参与这一激动人心的旅程。开发者可申请加入 Smart Widgets SDK 测试计划,开发属于自己的 Mini Apps,与 YakiHonne 的全球用户群共享成果。用户则可关注 YakiHonne 官方渠道(X或下载YakiHonne iOS/Android),体验链上互动与社交支付的全新可能。
-
 @ 3b3a42d3:d192e325
2025-04-10 08:57:51
@ 3b3a42d3:d192e325
2025-04-10 08:57:51Atomic Signature Swaps (ASS) over Nostr is a protocol for atomically exchanging Schnorr signatures using Nostr events for orchestration. This new primitive enables multiple interesting applications like:
- Getting paid to publish specific Nostr events
- Issuing automatic payment receipts
- Contract signing in exchange for payment
- P2P asset exchanges
- Trading and enforcement of asset option contracts
- Payment in exchange for Nostr-based credentials or access tokens
- Exchanging GMs 🌞
It only requires that (i) the involved signatures be Schnorr signatures using the secp256k1 curve and that (ii) at least one of those signatures be accessible to both parties. These requirements are naturally met by Nostr events (published to relays), Taproot transactions (published to the mempool and later to the blockchain), and Cashu payments (using mints that support NUT-07, allowing any pair of these signatures to be swapped atomically.
How the Cryptographic Magic Works 🪄
This is a Schnorr signature
(Zₓ, s):s = z + H(Zₓ || P || m)⋅kIf you haven't seen it before, don't worry, neither did I until three weeks ago.
The signature scalar s is the the value a signer with private key
k(and public keyP = k⋅G) must calculate to prove his commitment over the messagemgiven a randomly generated noncez(Zₓis just the x-coordinate of the public pointZ = z⋅G).His a hash function (sha256 with the tag "BIP0340/challenge" when dealing with BIP340),||just means to concatenate andGis the generator point of the elliptic curve, used to derive public values from private ones.Now that you understand what this equation means, let's just rename
z = r + t. We can do that,zis just a randomly generated number that can be represented as the sum of two other numbers. It also follows thatz⋅G = r⋅G + t⋅G ⇔ Z = R + T. Putting it all back into the definition of a Schnorr signature we get:s = (r + t) + H((R + T)ₓ || P || m)⋅kWhich is the same as:
s = sₐ + twheresₐ = r + H((R + T)ₓ || P || m)⋅ksₐis what we call the adaptor signature scalar) and t is the secret.((R + T)ₓ, sₐ)is an incomplete signature that just becomes valid by add the secret t to thesₐ:s = sₐ + tWhat is also important for our purposes is that by getting access to the valid signature s, one can also extract t from it by just subtracting
sₐ:t = s - sₐThe specific value of
tdepends on our choice of the public pointT, sinceRis just a public point derived from a randomly generated noncer.So how do we choose
Tso that it requires the secret t to be the signature over a specific messagem'by an specific public keyP'? (without knowing the value oft)Let's start with the definition of t as a valid Schnorr signature by P' over m':
t = r' + H(R'ₓ || P' || m')⋅k' ⇔ t⋅G = r'⋅G + H(R'ₓ || P' || m')⋅k'⋅GThat is the same as:
T = R' + H(R'ₓ || P' || m')⋅P'Notice that in order to calculate the appropriate
Tthat requirestto be an specific signature scalar, we only need to know the public nonceR'used to generate that signature.In summary: in order to atomically swap Schnorr signatures, one party
P'must provide a public nonceR', while the other partyPmust provide an adaptor signature using that nonce:sₐ = r + H((R + T)ₓ || P || m)⋅kwhereT = R' + H(R'ₓ || P' || m')⋅P'P'(the nonce provider) can then add his own signature t to the adaptor signaturesₐin order to get a valid signature byP, i.e.s = sₐ + t. When he publishes this signature (as a Nostr event, Cashu transaction or Taproot transaction), it becomes accessible toPthat can now extract the signaturetbyP'and also make use of it.Important considerations
A signature may not be useful at the end of the swap if it unlocks funds that have already been spent, or that are vulnerable to fee bidding wars.
When a swap involves a Taproot UTXO, it must always use a 2-of-2 multisig timelock to avoid those issues.
Cashu tokens do not require this measure when its signature is revealed first, because the mint won't reveal the other signature if they can't be successfully claimed, but they also require a 2-of-2 multisig timelock when its signature is only revealed last (what is unavoidable in cashu for cashu swaps).
For Nostr events, whoever receives the signature first needs to publish it to at least one relay that is accessible by the other party. This is a reasonable expectation in most cases, but may be an issue if the event kind involved is meant to be used privately.
How to Orchestrate the Swap over Nostr?
Before going into the specific event kinds, it is important to recognize what are the requirements they must meet and what are the concerns they must address. There are mainly three requirements:
- Both parties must agree on the messages they are going to sign
- One party must provide a public nonce
- The other party must provide an adaptor signature using that nonce
There is also a fundamental asymmetry in the roles of both parties, resulting in the following significant downsides for the party that generates the adaptor signature:
- NIP-07 and remote signers do not currently support the generation of adaptor signatures, so he must either insert his nsec in the client or use a fork of another signer
- There is an overhead of retrieving the completed signature containing the secret, either from the blockchain, mint endpoint or finding the appropriate relay
- There is risk he may not get his side of the deal if the other party only uses his signature privately, as I have already mentioned
- There is risk of losing funds by not extracting or using the signature before its timelock expires. The other party has no risk since his own signature won't be exposed by just not using the signature he received.
The protocol must meet all those requirements, allowing for some kind of role negotiation and while trying to reduce the necessary hops needed to complete the swap.
Swap Proposal Event (kind:455)
This event enables a proposer and his counterparty to agree on the specific messages whose signatures they intend to exchange. The
contentfield is the following stringified JSON:{ "give": <signature spec (required)>, "take": <signature spec (required)>, "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>", "description": "<Info about the proposal (optional)>", "nonce": "<Signature public nonce (optional)>", "enc_s": "<Encrypted signature scalar (optional)>" }The field
roleindicates what the proposer will provide during the swap, either the nonce or the adaptor. When this optional field is not provided, the counterparty may decide whether he will send a nonce back in a Swap Nonce event or a Swap Adaptor event using thenonce(optionally) provided by in the Swap Proposal in order to avoid one hop of interaction.The
enc_sfield may be used to store the encrypted scalar of the signature associated with thenonce, since this information is necessary later when completing the adaptor signature received from the other party.A
signature specspecifies thetypeand all necessary information for producing and verifying a given signature. In the case of signatures for Nostr events, it contain a template with all the fields, exceptpubkey,idandsig:{ "type": "nostr", "template": { "kind": "<kind>" "content": "<content>" "tags": [ … ], "created_at": "<created_at>" } }In the case of Cashu payments, a simplified
signature specjust needs to specify the payment amount and an array of mints trusted by the proposer:{ "type": "cashu", "amount": "<amount>", "mint": ["<acceptable mint_url>", …] }This works when the payer provides the adaptor signature, but it still needs to be extended to also work when the payer is the one receiving the adaptor signature. In the later case, the
signature specmust also include atimelockand the derived public keysYof each Cashu Proof, but for now let's just ignore this situation. It should be mentioned that the mint must be trusted by both parties and also support Token state check (NUT-07) for revealing the completed adaptor signature and P2PK spending conditions (NUT-11) for the cryptographic scheme to work.The
tagsare:"p", the proposal counterparty's public key (required)"a", akind:30455Swap Listing event or an application specific version of it (optional)
Forget about this Swap Listing event for now, I will get to it later...
Swap Nonce Event (kind:456) - Optional
This is an optional event for the Swap Proposal receiver to provide the public nonce of his signature when the proposal does not include a nonce or when he does not want to provide the adaptor signature due to the downsides previously mentioned. The
contentfield is the following stringified JSON:{ "nonce": "<Signature public nonce>", "enc_s": "<Encrypted signature scalar (optional)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Swap Adaptor Event (kind:457)
The
contentfield is the following stringified JSON:{ "adaptors": [ { "sa": "<Adaptor signature scalar>", "R": "<Signer's public nonce (including parity byte)>", "T": "<Adaptor point (including parity byte)>", "Y": "<Cashu proof derived public key (if applicable)>", }, …], "cashu": "<Cashu V4 token (if applicable)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Discoverability
The Swap Listing event previously mentioned as an optional tag in the Swap Proposal may be used to find an appropriate counterparty for a swap. It allows a user to announce what he wants to accomplish, what his requirements are and what is still open for negotiation.
Swap Listing Event (kind:30455)
The
contentfield is the following stringified JSON:{ "description": "<Information about the listing (required)>", "give": <partial signature spec (optional)>, "take": <partial signature spec (optional)>, "examples: [<take signature spec>], // optional "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>" }The
descriptionfield describes the restrictions on counterparties and signatures the user is willing to accept.A
partial signature specis an incompletesignature specused in Swap Proposal eventskind:455where omitting fields signals that they are still open for negotiation.The
examplesfield is an array ofsignature specsthe user would be willing totake.The
tagsare:"d", a unique listing id (required)"s", the status of the listingdraft | open | closed(required)"t", topics related to this listing (optional)"p", public keys to notify about the proposal (optional)
Application Specific Swap Listings
Since Swap Listings are still fairly generic, it is expected that specific use cases define new event kinds based on the generic listing. Those application specific swap listing would be easier to filter by clients and may impose restrictions and add new fields and/or tags. The following are some examples under development:
Sponsored Events
This listing is designed for users looking to promote content on the Nostr network, as well as for those who want to monetize their accounts by sharing curated sponsored content with their existing audiences.
It follows the same format as the generic Swap Listing event, but uses the
kind:30456instead.The following new tags are included:
"k", event kind being sponsored (required)"title", campaign title (optional)
It is required that at least one
signature spec(giveand/ortake) must have"type": "nostr"and also contain the following tag["sponsor", "<pubkey>", "<attestation>"]with the sponsor's public key and his signature over the signature spec without the sponsor tag as his attestation. This last requirement enables clients to disclose and/or filter sponsored events.Asset Swaps
This listing is designed for users looking for counterparties to swap different assets that can be transferred using Schnorr signatures, like any unit of Cashu tokens, Bitcoin or other asset IOUs issued using Taproot.
It follows the same format as the generic Swap Listing event, but uses the
kind:30457instead.It requires the following additional tags:
"t", asset pair to be swapped (e.g."btcusd")"t", asset being offered (e.g."btc")"t", accepted payment method (e.g."cashu","taproot")
Swap Negotiation
From finding an appropriate Swap Listing to publishing a Swap Proposal, there may be some kind of negotiation between the involved parties, e.g. agreeing on the amount to be paid by one of the parties or the exact content of a Nostr event signed by the other party. There are many ways to accomplish that and clients may implement it as they see fit for their specific goals. Some suggestions are:
- Adding
kind:1111Comments to the Swap Listing or an existing Swap Proposal - Exchanging tentative Swap Proposals back and forth until an agreement is reached
- Simple exchanges of DMs
- Out of band communication (e.g. Signal)
Work to be done
I've been refining this specification as I develop some proof-of-concept clients to experience its flaws and trade-offs in practice. I left the signature spec for Taproot signatures out of the current document as I still have to experiment with it. I will probably find some important orchestration issues related to dealing with
2-of-2 multisig timelocks, which also affects Cashu transactions when spent last, that may require further adjustments to what was presented here.The main goal of this article is to find other people interested in this concept and willing to provide valuable feedback before a PR is opened in the NIPs repository for broader discussions.
References
- GM Swap- Nostr client for atomically exchanging GM notes. Live demo available here.
- Sig4Sats Script - A Typescript script demonstrating the swap of a Cashu payment for a signed Nostr event.
- Loudr- Nostr client under development for sponsoring the publication of Nostr events. Live demo available at loudr.me.
- Poelstra, A. (2017). Scriptless Scripts. Blockstream Research. https://github.com/BlockstreamResearch/scriptless-scripts
-
 @ 20986fb8:cdac21b3
2025-04-10 08:52:37
@ 20986fb8:cdac21b3
2025-04-10 08:52:37Social apps are entering a new era, evolving from traditional centralized platforms to decentralized ecosystems. Users increasingly demand lightweight, intelligent, and privacy-focused applications. In this shift, Mini Apps have emerged as a mainstream choice for social applications, thanks to their rapid development, flexible deployment, and decentralized nature. The rise of cryptocurrency payments has further fueled this trend, offering low-cost, borderless, and financially liberating solutions that significantly lower transaction barriers and drive the scalability of Mini Apps. As one of the most popular decentralized social payment clients on the Bitcoin ecosystem’s Nostr protocol, YakiHonne has earned a global reputation for its exceptional user experience and seamless social payment features, reaching over 170 countries. Now, YakiHonne is set to launch its programmable Smart Widgets—a developer toolkit for Mini Apps. This product will redefine how users interact and transact on social platforms, bringing fresh energy to the on-chain app ecosystem and social payments.
Smart Widgets: A Game-Changer for Social and On-Chain Consumption
YakiHonne Smart Widgets are programmable mini-apps embedded within social feeds, enabling users to effortlessly make on-chain payments, engage in interactions, and perform actions without leaving their content stream. More than just a tool, Smart Widgets serve as an open, decentralized app store, empowering both users and developers with unparalleled creativity and flexibility.
Smart Widgets come in three user-friendly formats to meet diverse needs:
- Basic Widgets: Anyone can create these using an intuitive editor—just pick a template, add content, and generate features like zap, minting, or voting. Users can interact with these actions directly in their feed with a single click, enjoying a fast, seamless experience.
- Action Widgets: Users can quickly create these by embedding app links, no coding required. With a single tap on a button in the feed, users can access external decentralized apps (like exchanges) right within the interface, ensuring a smooth, uninterrupted experience.
- Tool Widgets (Mini Apps): Designed for developers or users with coding skills, these are built using the Smart Widgets SDK to create more advanced apps with complex on-chain operations. Users can perform tasks like data queries, on-chain actions, gaming, or instant payments directly in their social feed, with a highly integrated and fluid experience.
Key Features:
- Rapid Development: Developers can turn ideas into reality in just hours, using familiar web technologies to create near-native app experiences—no lengthy app store reviews required.
- Social Login: Users can access Mini Apps without usernames or passwords, using their Nostr/YakiHonne identity to interact seamlessly within their social feed, making the experience more connected and effortless.
- Easy Discovery and Retention: With one-tap discovery through social feeds, built-in viral growth mechanics, and a Mini App store for more options, users can explore new apps effortlessly. They can save favorites and get notifications to return for more.
- Instant Interaction and Consumption: Mini Apps integrate seamlessly with YakiHonne’s social payment infrastructure, allowing users to pay, vote, or play games without leaving their feed. Social engagement and on-chain actions blend naturally, with consumption woven effortlessly into every interaction.
Transforming Daily Experiences: Smart Widgets in Action
YakiHonne Smart Widgets bridge social engagement and on-chain consumption, delivering a wide range of use cases: - On-Chain Interactions: While browsing their feed, users can join on-chain votes or play lightweight games through Smart Widgets—like casting a vote on a community proposal or challenging a friend to a quick game, all without leaving the app. - Smart Agents: Users can leverage Agent Widgets to auto-create and share content, such as personalized posts or short videos, powering an AI-driven media experience. - DAO Governance: Using aMACI for anonymous voting, combined with Agent Widgets for autonomous governance, users can participate in DAO decisions directly within their feed, fostering decentralized community growth. - Social Zap: Users can send small tips through their feed, like rewarding a friend’s post with an on-chain token, sparking more engagement and driving consumption. - Content Subscriptions: Support creators or apps with ongoing subscriptions—users can subscribe to their favorite services with one tap, enjoying a seamless renewal experience.
These scenarios not only boost user engagement and convenience but also open new growth opportunities for creators, developers, and communities.
Shaping the Future: The Ecosystem Impact of Smart Widgets
YakiHonne Smart Widgets are poised to transform the on-chain app ecosystem and social payments. They provide an open platform for developers, enabling anyone to deploy innovative apps quickly and enrich YakiHonne’s ecosystem. YakiHonne’s social payment infrastructure further empowers Mini Apps by offering efficient payment support, reducing integration costs for developers while ensuring a secure, seamless transaction experience for users. This support accelerates the commercialization of Mini Apps and fuels the growth of on-chain consumption.
For users, Smart Widgets seamlessly blend social interaction with consumption, creating an immersive and practical digital experience. For creators and communities, they offer a low-barrier entry to on-chain opportunities, helping them connect with a global audience. This product isn’t just a technological leap—it’s a glimpse into the future of decentralized lifestyles. YakiHonne is committed to building an open, vibrant social and consumption ecosystem through Smart Widgets, where every interaction sparks on-chain value.
Join the Future: Explore Smart Widgets Today
YakiHonne invites users and developers worldwide to join this exciting journey. Developers can apply to join the Smart Widgets SDK testing program, creating their own Mini Apps and tapping into YakiHonne’s global user base. Users can follow YakiHonne on official channels –X or download the YakiHonne iOS/Android app– to experience the next generation of on-chain interactions and social payments.
YakiHonne Programmable Smart Widgets are set to launch a new chapter for social and on-chain consumption. Let’s embrace this transformation together!
-
 @ 866e0139:6a9334e5
2025-04-10 06:42:26
@ 866e0139:6a9334e5
2025-04-10 06:42:26
Autor: Sepp Kusstatscher. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Aus moralischen Gründen sollen alle Menschen guten Willens aufgerufen werden, aktiv für Frieden zu kämpfen. Die pauschale Verteufelung von Putin und Trump führt uns in eine Massenpsychose und schlussendlich in einen Dritten Weltkrieg. Würden wir die Mütter dieser Welt fragen, gäbe es eine übergroße Mehrheit für den Frieden. Die Ex-Verteidigungsministerin Ursula von der Leyen wäre dann wohl bei einer verschwindend kleinen Minderheit.
Wir sollten doch einmal die 18- bis 30-Jährigen fragen, ob sie bereit wären, in einen Krieg zu ziehen, der von vorwiegend alten und nicht mehr wehrfähigen Männern angezettelt wird! Würden die Aktionäre der Waffenindustrie und deren Söhne gezwungen, bei allen kriegerischen Auseinandersetzungen auf der Welt in der ersten Reihe vorne zu kämpfen, dann gäbe es wohl überhaupt keine Kriege mehr.
Die Gesellschaft ist krank im Gehirn, wenn die Rüstungs-, Pharma- und Chemie-Industrie die „gesündesten“ Wirtschaftsbereiche sind. Die USA, die treibende Kraft der NATO, dürften nach so vielen Angriffskriegen in den letzten Jahrzehnten das Wort Verteidigungspolitik als Rechtfertigung für Aufrüstung nie in den Mund nehmen.
Aus humanen, ökonomischen und ökologischen Gründen ist ein Krieg nie und nimmer zu rechtfertigen.
- Wir als Menschheitsfamilie müssen die vielen Konflikte ohne Gewalt lösen.
- Die Verschuldung der öffentlichen Hand durch das Aufrüsten zerstört den allgemeinen Wohlstand.
- Wohl keine andere Aktivität beschleunigt den Klimawandel stärker als Kriege.
Auf wen sollten wir hören? Auf Ethiker und auf Friedensforscher und nicht auf Militärexperten und Wirtschaftskapitäne! Denken wir an die Goldene Regel der Weltethik!
Was brauchen wir dringend? Intensive diplomatische Bemühungen und kein Angst erregendes Säbelrasseln! Viktor Orbán, dessen autoritärer Führungsstil kritisiert werden muss, hat in den ersten Tagen seiner EU-Ratspräsidentschaft eines goldrichtig gemacht: Er hat mit den Machthabern in der Ukraine, in Russland, in China und in den USA geredet.
Die EU der 27 Nationalstaaten zerstört sich selbst. Das wunderbare Friedensprojekt Europa wird durch den derzeitigen Mainstream in Politik und in den Medien kaputt gemacht. Menschen mit Verstand und Herz sind entsetzt. In der Schule haben wir gelernt, dass Europa von Gibraltar bis zum Ural reicht. Der Keil, der zwischen Deutschland und Russland hineingetrieben wurde, trotz der schlimmsten Erfahrungen im Zweiten Weltkrieg, ist des Teufels. Die Grußformel „Pax – Friede!“ der Christen, „Schalom!“ der Juden und „Salam!“ der Moslems muss viel mehr sein als nur eine Floskel!
Der Aufruf von Immanuel Kant im Büchlein „Zum ewigen Frieden“ und das heilige Versprechen nach 1945 „Nie wieder Krieg!“ sind ein Imperativ zum Abrüsten und ein Aufruf, Schwerter zu Pflugscharen zu schmieden.
Frieden ist möglich, kann aber sicher nicht mit Waffengewalt herbeigeführt werden.
Lassen wir doch die Friedenstaube fliegen!
Der Südtiroler Politiker Sepp Kusstatscher, geboren 1947 in Villanders, studierte Philosophie, Theologie und Pädagogik und war viele Jahre im Bereich der Erwachsenenbildung und beruflichen Weiterbildung tätig, u. a. 17 Jahre als Leiter der Berufsschulen von Brixen. Von 1974 bis 1985 war er Bürgermeister seiner Heimatgemeinde Villanders, von 1988 bis 1993 Abgeordneter zum Südtiroler Landtag und von 2004 bis 2009 Mitglied des Europäischen Parlaments. Homepage: https://kusstatscher.net/
Die Friedenstaube fliegt auch in Ihr Postfach!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst an alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 57d1a264:69f1fee1
2025-04-10 05:54:45
@ 57d1a264:69f1fee1
2025-04-10 05:54:45Some banners to promote ~Design territory in the Wild Web. Interested to kand feedback now your thought on it.
| Banner | Content | |---|---| |
| Stop scrolling, start stacking! Your #insights, your #stories, your #code – they have real #value. On #StackerNews #Design, we believe in rewarding #quality contents. Turn your #passion and #knowledge into #Bitcoin. Share your v#oice and get rewarded for it, join the conversation! Explore now: https://stacker.news/~Design/r/Design_r #Bitcoin #LightningNetwork #Community #ContentCreation #EarnBitcoin #Tech #SNdesign | |
| Stop scrolling, start flourishing! Your unique 3perspective, your groundbreaking #ideas, your niche #knowledge – it all has #value. On #StackerNews #Design we #reward you with #Bitcoin, instantly via the #LightningNetwork. Don't let your #insights fade into the #digital noise. Join a community that values #contribution, fuels #innovation, and puts the #power back in your #diamondhands (and #wallet!). Turn your thoughts into #zaps? Join the conversation: https://stacker.news/~Design/r/Design_r #Bitcoin #Lightning #Network #Community #EarnBitcoin #Tech #Design #Innovation #ContentCreation #Crypto | |
| Stop scrolling, #stack #sats for your #insights! #StackerNews #Design is where your #creative spark meets the #LightningNetwork. Discuss #ideas, share your #work, and #earn #Bitcoin for valuable contributions. Join a vibrant #community shaping the #future of #creativity and #tech, one #zap at a time. Explore the intersection of #innovation and #functionality https://stacker.news/~Design/r/Design_r #StackerNews #BitcoinDesign #DesignCommunity #Lightning #Network #UIDesign #UXDesign #Crypto #EarnBitcoin | |
| Stop scrolling, start stacking #sats! Talk #Design on #StackerNews – the platform where your #insights on #Tech, #Design, #Finance, #econ, #Food #DIY and more actually earn you real #Bitcoin via the #LightningNetwork. Join a vibrant #community, #discover diverse #perspectives, and #EarnBitcoin for sharing valuable content. Explore the #future of #contentCreation: https://stacker.news/~Design/r/Design_r #StackerNews #Lightning #Network #Crypto #Tech #Finance #Design #ContentCreator #GetPaidInBitcoin #SocialMedia #Community #BitconAccepted | |
| #StackerNews #Design is where your engagement actually #pays. #Earn #Bitcoin instantly via #zaps just for sharing great unique #content and joining #discussions on everything from #innovative #tech to #creative #ideas. Discover diverse #opinion, connect with a #community, start #earning. Join the #future of content: https://stacker.news/~Design/r/Design_r #LightningNetwork #EarnBitcoin #CryptoCommunity #ContentCreators #StackerNews #Decentralized #SocialMedia |
originally posted at https://stacker.news/items/939548
-
 @ c1e9ab3a:9cb56b43
2025-04-10 02:58:16
@ c1e9ab3a:9cb56b43
2025-04-10 02:58:16Assumptions
| Factor | Assumption | |--------|------------| | CO₂ | Not considered a pollutant or is captured/stored later | | Water Use | Regulated across all sources; cooling towers or dry cooling required | | Compliance Cost | Nuclear no longer burdened by long licensing and construction delays | | Coal Waste | Treated as valuable raw material (e.g., fly ash for cement, gypsum from scrubbers) | | Nuclear Tech | Gen IV SMRs in widespread use (e.g., 50–300 MWe units, modular build, passive safety) | | Grid Role | All three provide baseload or load-following power | | Fuel Pricing | Moderate and stable (no energy crisis or supply chain disruptions) |
Performance Comparison
| Category | Coal (IGCC + Scrubbers) | Natural Gas (CCGT) | Nuclear (Gen IV SMRs) | |---------|-----------------------------|------------------------|--------------------------| | Thermal Efficiency | 40–45% | 55–62% | 30–35% | | CAPEX ($/kW) | $3,500–5,000 | $900–1,300 | $4,000–7,000 (modularized) | | O&M Cost ($/MWh) | $30–50 | $10–20 | $10–25 | | Fuel Cost ($/MWh) | $15–25 | $25–35 | $6–10 | | Water Use (gal/MWh) | 300–500 (with cooling towers) | 100–250 | 300–600 | | Air Emissions | Very low (excluding CO₂) | Very low | None | | Waste | Usable (fly ash, FGD gypsum, slag) | Minimal | Compact, long-term storage required | | Ramp/Flexibility | Slow ramp (newer designs better) | Fast ramp | Medium (SMRs better than traditional) | | Footprint (Land & Supply) | Large (mining, transport) | Medium | Small | | Energy Density | Medium | Medium-high | Very high | | Build Time | 4–7 years | 2–4 years | 2–5 years (with factory builds) | | Lifecycle (years) | 40+ | 30+ | 60+ | | Grid Resilience | High | High | Very High (passive safety, long refuel) |
Strategic Role Summary
1. Coal (Clean & Integrated)
- Strengths: Long-term fuel security; byproduct reuse; high reliability; domestic resource.
- Drawbacks: Still low flexibility; moderate efficiency; large physical/logistical footprint.
- Strategic Role: Best suited for regions with abundant coal and industrial reuse markets.
2. Natural Gas (CCGT)
- Strengths: High efficiency, low CAPEX, grid agility, low emissions.
- Drawbacks: Still fossil-based; dependent on well infrastructure; less long-lived.
- Strategic Role: Excellent transitional and peaking solution; strong complement to renewables.
3. Nuclear (Gen IV SMRs)
- Strengths: Highest energy density; no air emissions or CO₂; long lifespan; modular & scalable.
- Drawbacks: Still needs safe waste handling; high upfront cost; novel tech in deployment stage.
- Strategic Role: Ideal for low-carbon baseload, remote areas, and national strategic assets.
Adjusted Levelized Cost of Electricity (LCOE)
| Source | LCOE ($/MWh) | Notes | |--------|------------------|-------| | Coal (IGCC w/scrubbers) | ~$75–95 | Lower with valuable waste | | Natural Gas (CCGT) | ~$45–70 | Highly competitive if fuel costs are stable | | Gen IV SMRs | ~$65–85 | Assuming factory production and streamlined permitting |
Final Verdict (Under Optimized Assumptions)
- Most Economical Short-Term: Natural Gas
- Most Strategic Long-Term: Gen IV SMRs
- Most Viable if Industrial Ecosystem Exists: Clean Coal
All three could coexist in a diversified, stable energy grid: - Coal filling a regional or industrial niche, - Gas providing flexibility and economy, - SMRs ensuring long-term sustainability and energy security.
-
 @ c1e9ab3a:9cb56b43
2025-04-10 02:57:02
@ c1e9ab3a:9cb56b43
2025-04-10 02:57:02A follow-up to nostr:naddr1qqgxxwtyxe3kvc3jvvuxywtyxs6rjq3qc856kwjk524kef97hazw5e9jlkjq4333r6yxh2rtgefpd894ddpsxpqqqp65wuaydz8
This whitepaper, a comparison of baseload power options, explores a strategic policy framework to reduce the cost of next-generation nuclear power by aligning Gen IV Small Modular Reactors (SMRs) with national security objectives, public utility management, and a competitive manufacturing ecosystem modeled after the aerospace industry. Under this approach, SMRs could deliver stable, carbon-free power at $40–55/MWh, rivaling the economics of natural gas and renewables.
1. Context and Strategic Opportunity
Current Nuclear Cost Challenges
- High capital expenditure ($4,000–$12,000/kW)
- Lengthy permitting and construction timelines (10–15 years)
- Regulatory delays and public opposition
- Customized, one-off reactor designs with no economies of scale
The Promise of SMRs
- Factory-built, modular units
- Lower absolute cost and shorter build time
- Enhanced passive safety
- Scalable deployment
2. National Security as a Catalyst
Strategic Benefits
- Energy resilience for critical defense infrastructure
- Off-grid operation and EMP/cyber threat mitigation
- Long-duration fuel cycles reduce logistical risk
Policy Implications
- Streamlined permitting and site access under national defense exemptions
- Budget support via Department of Defense and Department of Energy
- Co-location on military bases and federal sites
3. Publicly Chartered Utilities: A New Operating Model
Utility Framework
- Federally chartered, low-margin operator (like TVA or USPS)
- Financially self-sustaining through long-term PPAs
- Focus on reliability, security, and public service over profit
Cost Advantages
- Lower cost of capital through public backing
- Predictable revenue models
- Community trust and stakeholder alignment
4. Competitive Manufacturing: The Aviation Analogy
Model Characteristics
- Multiple certified vendors, competing under common safety frameworks
- Factory-scale production and supply chain specialization
- Domestic sourcing for critical components and fuel
Benefits
- Cost reductions from repetition and volume
- Innovation through competition
- Export potential and industrial job creation
5. Levelized Cost of Electricity (LCOE) Impact
| Cost Lever | Estimated LCOE Reduction | |------------|--------------------------| | Streamlined regulation | -10 to -20% | | Public-charter operation | -5 to -15% | | Factory-built SMRs | -15 to -30% | | Defense market anchor | -10% |
Estimated Resulting LCOE: $40–55/MWh
6. Strategic Outcomes
- Nuclear cost competitiveness with gas and renewables
- Decarbonization without reliability sacrifice
- Strengthened national energy resilience
- Industrial and workforce revitalization
- U.S. global leadership in clean, secure nuclear energy
7. Recommendations
- Create a public-private chartered SMR utility
- Deploy initial reactors on military and federal lands
- Incentivize competitive SMR manufacturing consortia
- Establish fast-track licensing for Gen IV designs
- Align DoD/DOE energy procurement to SMR adoption
Conclusion
This strategy would transform nuclear power from a high-cost, high-risk sector into a mission-driven, economically viable backbone of American energy and defense infrastructure. By treating SMRs as strategic assets, not just energy projects, the U.S. can unlock affordable, scalable, and secure nuclear power for generations to come.
-
 @ c1e9ab3a:9cb56b43
2025-04-10 02:55:11
@ c1e9ab3a:9cb56b43
2025-04-10 02:55:11The United States is on the cusp of a historic technological renaissance, often referred to as the Fourth Industrial Revolution. Artificial intelligence, automation, advanced robotics, quantum computing, biotechnology, and clean manufacturing are converging into a seismic shift that will redefine how we live, work, and relate to one another. But there's a critical catch: this transformation depends entirely on the availability of stable, abundant, and inexpensive electricity.
Why Electricity is the Keystone of Innovation
Let’s start with something basic but often overlooked. Every industrial revolution has had an energy driver:
- The First rode the steam engine, powered by coal.
- The Second was electrified through centralized power plants.
- The Third harnessed computing and the internet.
- The Fourth will demand energy on a scale and reliability never seen before.
Imagine a city where thousands of small factories run 24/7 with robotics and AI doing precision manufacturing. Imagine a national network of autonomous vehicles, delivery drones, urban vertical farms, and high-bandwidth communication systems. All of this requires uninterrupted and inexpensive power.
Without it? Costs balloon. Innovation stalls. Investment leaves. And America risks becoming a second-tier economic power in a multipolar world.
So here’s the thesis: If we want to lead the Fourth Industrial Revolution, we must first lead in energy. And nuclear — specifically Gen IV Small Modular Reactors (SMRs) — must be part of that leadership.
The Nuclear Case: Clean, Scalable, Strategic
Let’s debunk the myth: nuclear is not the boogeyman of the 1970s. It’s one of the safest, cleanest, and most energy-dense sources we have.
But traditional nuclear has problems:
- Too expensive to build.
- Too long to license.
- Too bespoke and complex.
Enter Gen IV SMRs:
- Factory-built and transportable.
- Passively safe with walk-away safety designs.
- Scalable in 50–300 MWe increments.
- Ideal for remote areas, industrial parks, and military bases.
But even SMRs will struggle under the current regulatory, economic, and manufacturing ecosystem. To unlock their potential, we need a new national approach.
The Argument for National Strategy
Let’s paint a vision:
SMRs deployed at military bases across the country, secured by trained personnel, powering critical infrastructure, and feeding clean, carbon-free power back into surrounding communities.
SMRs operated by public chartered utilities—not for Wall Street profits, but for stability, security, and public good.
SMRs manufactured by a competitive ecosystem of certified vendors, just like aircraft or medical devices, with standard parts and rapid regulatory approval.
This isn't science fiction. It's a plausible, powerful model. Here’s how we do it.
Step 1: Treat SMRs as a National Security Asset
Why does the Department of Defense spend billions to secure oil convoys and build fuel depots across the world, but not invest in nuclear microgrids that would make forward bases self-sufficient for decades?
Nuclear power is inherently a strategic asset:
- Immune to price shocks.
- Hard to sabotage.
- Decades of stable power from a small footprint.
It’s time to reframe SMRs from an energy project to a national security platform. That changes everything.
Step 2: Create Public-Chartered Operating Companies
We don’t need another corporate monopoly or Wall Street scheme. Instead, let’s charter SMR utilities the way we chartered the TVA or the Postal Service:
- Low-margin, mission-oriented.
- Publicly accountable.
- Able to sign long-term contracts with DOD, DOE, or regional utilities.
These organizations won’t chase quarterly profits. They’ll chase uptime, grid stability, and national resilience.
Step 3: Build a Competitive SMR Industry Like Aerospace
Imagine multiple manufacturers building SMRs to common, certified standards. Components sourced from a wide supplier base. Designs evolving year over year, with upgrades like software and avionics do.
This is how we build:
- Safer reactors
- Cheaper units
- Modular designs
- A real export industry
Airplanes are safe, affordable, and efficient because of scale and standardization. We can do the same with reactors.
Step 4: Anchor SMRs to the Coming Fourth Industrial Revolution
AI, robotics, and distributed manufacturing don’t need fossil fuels. They need cheap, clean, continuous electricity.
- AI datacenters
- Robotic agriculture
- Carbon-free steel and cement
- Direct air capture
- Electric industrial transport
SMRs enable this future. And they decentralize power, both literally and economically. That means jobs in every region, not just coastal tech hubs.
Step 5: Pair Energy Sovereignty with Economic Reform
Here’s the big leap: what if this new energy architecture was tied to a transparent, auditable, and sovereign monetary system?
- Public utilities priced in a new digital dollar.
- Trade policy balanced by low-carbon energy exports.
- Public accounting verified with open ledgers.
This is not just national security. It’s monetary resilience.
The world is moving to multi-polar trade systems. Energy exports and energy reliability will define economic influence. If America leads with SMRs, we lead the conversation.
Conclusion: A Moral and Strategic Imperative
We can either:
- Let outdated fears and bureaucracy stall the future, or...
- Build the infrastructure for clean, secure, and sovereign prosperity.
We have the designs.
We have the talent.
We have the need.What we need now is will.
The Fourth Industrial Revolution will either be powered by us—or by someone else. Let’s make sure America leads. And let’s do it with SMRs, public charter, competitive industry, and national purpose.
It’s time.
This is a call to engineers, legislators, veterans, economists, and every American who believes in building again. SMRs are not just about power. They are about sovereignty, security, and shared prosperity.
Further reading:
nostr:naddr1qqgrjv33xenx2drpve3kxvrp8quxgqgcwaehxw309anxjmr5v4ezumn0wd68ytnhd9hx2tczyrq7n2e62632km9yh6l5f6nykt76gzkxxy0gs6agddr9y95uk445xqcyqqq823cdzc99s
-
 @ 502ab02a:a2860397
2025-04-10 01:47:24
@ 502ab02a:a2860397
2025-04-10 01:47:24เมื่อวานโพสเรื่องบรอกโคลีฝีมือมนุษย์แล้ว มีคนสงสัยว่าตกลงมันดีไหม เวลาพูดถึงอาหารสุขภาพ ภาพที่ลอยมาในหัวของหลายๆ คนคงหนีไม่พ้น "บรอกโคลีลวก" สีเขียวสดใส เสิร์ฟคู่ไข่ต้มขาวๆ หรืออกไก่นุ่มนิ่มในกล่อง meal prep แต่ก่อนจะตักเข้าปาก เราลองตั้งคำถามง่ายๆ ก่อนว่า… “บรอกโคลีเกิดขึ้นในธรรมชาติไหม?” คำตอบคือ ไม่ เลยครับ
บรอกโคลีไม่ได้เกิดจากการงอกงามของเมล็ดในป่า หรือเติบโตตามชายเขาเหมือนพืชสมุนไพรหรือผลไม้ดั้งเดิม แต่มันคือพืชที่มนุษย์ สร้างขึ้นมา ผ่านการคัดสายพันธุ์อย่างตั้งใจให้ได้รูปร่าง กลิ่น สี และรสชาติที่ต้องการ โดยมีจุดเริ่มต้นจากพืชตระกูลเดียวกันกับ “มัสตาร์ดป่า (wild mustard)” ซึ่งเป็นพืชที่แทบไม่มีใครกิน มนุษย์ใช้วิธีเลือกต้นที่มีลักษณะ “หัวดอกใหญ่” มาเพาะซ้ำๆ จนกลายเป็นบรอกโคลี ในขณะที่พืชอีกกิ่งสายพันธุ์จากต้นเดียวกัน กลายร่างไปเป็น กะหล่ำปลี กะหล่ำดอก คะน้า และใบมัสตาร์ด
ฟังไม่ผิด ทั้งหมดนี้คือ “ญาติกัน” จากพืชป่าต้นเดียวกัน และเป็น ผลผลิตของการทดลองจากมนุษย์ ไม่ใช่ธรรมชาติ มันคือ “ของใหม่” ที่เราเพิ่งรู้จักในช่วง 100–150 ปีหลังนี้เอง
แล้วอะไรที่ทำให้บรอกโคลีกลายเป็นอาหารสุขภาพ? หนึ่งในคำตอบคือ ภาพลักษณ์ (branding) บรอกโคลีถูกผลักดันในยุคหลังสงครามโลกโดยรัฐบาลสหรัฐฯ เพื่อโปรโมท “การกินผักเพื่อสุขภาพ” และเป็นพืชที่ปลูกง่าย อดทน ขนส่งสะดวก
อุตสาหกรรมอาหารก็โหนกระแส ผนวกกับงานวิจัยที่เลือกตีแผ่ “ประโยชน์เฉพาะด้าน” ของสารบางตัวอย่างเช่น ซัลโฟราเฟน (sulforaphane) ที่ได้จากกลูโคซิโนเลต (glucosinolate) ในบรอกโคลี ซึ่งมีฤทธิ์กระตุ้นเอ็นไซม์ล้างพิษในตับ
แต่นั่นเป็นแค่ด้านเดียวของเหรียญ…
บรอกโคลียังมีสารในกลุ่มเดียวกันนี้ที่ ต่อต้านการดูดซึมไอโอดีน ทำให้ไทรอยด์เฉื่อยได้ในบางคน ยังไม่รวมถึงความยากในการย่อย ก่อแก๊สในลำไส้ และอาจทำให้เกิดอาการแพ้ในกลุ่มคนที่ระบบภูมิคุ้มกันไวเกิน นอกจากนี้ที่บอกไปแล้วว่า มันไม่ใช่ธรรมชาติ เราเลยไม่สามารถพบบรอกโคลีได้ในป่า มันต้องเกิดจากการปลูกเท่านั้น นั่นแน่ ตาสีส้มเริ่มทำงาน
บรอกโคลี “ไม่มีเมล็ด” แบบธรรมชาติ เพราะมันไม่ได้เกิดจากธรรมชาติแท้ๆ แต่นั่นไม่ได้แปลว่าเราปลูกมันไม่ได้เพราะ “เมล็ดของบรอกโคลีมีนะ แต่เป็นเมล็ดที่ได้จากต้นพันธุ์ที่มนุษย์คัดแยกและควบคุมการผสมพันธุ์มาแล้ว”
บริษัทเมล็ดพันธุ์ระดับโลก อย่าง Monsanto, Syngenta, Bayer ฯลฯ จะพัฒนาเมล็ดที่ผ่านการผสมสายพันธุ์แบบ "F1 Hybrid" ซึ่งหมายความว่าเขาจะเอาพ่อแม่พันธุ์เฉพาะที่คัดเลือกไว้ มาผสมกันเพื่อให้ได้ลูกบรอกโคลีที่มีลักษณะตรงตามต้องการ เช่น ดอกแน่น สีเขียวเข้ม โตเร็ว ต้านทานโรค เมล็ดบรอกโคลีจึงเป็น เมล็ดลูกผสมรุ่นแรก (F1) ซึ่งเกษตรกร ไม่สามารถเก็บเมล็ดจากต้นบรอกโคลีที่ปลูกไว้เอง แล้วปลูกต่อได้ เพราะถ้าเอาไปปลูกใหม่รุ่นถัดไป (F2) ลักษณะจะเริ่มแปรปรวน แตกแถว ดอกเล็กลง หรือกลายพันธุ์ ดังนั้น ทุกปี เกษตรกรต้องซื้อเมล็ดใหม่จากบริษัทผู้ผลิต ซึ่งนี่แหละคือระบบ seed monopoly หรือ เศรษฐกิจผูกขาดพันธุ์พืช ที่ควบคุมโดยบริษัทยักษ์ใหญ่ เอาไว้จะมาขยายความมุมนี้ให้อีกทีครับ
ส่วนเรื่องสารอาหารความอาหารคลีนเค้าว่าดี ต้องมาเคลียร์ mind set กันอีกทีในนี้ คือในโลกของพืชนั้น การเอาตัวรอดไม่ใช่เรื่องเล่น ๆ เพราะพวกมันวิ่งหนีไม่ได้ ไม่มีกรงเล็บ ไม่มีเสียงคำราม มีแค่ “เคมี” เป็นอาวุธ และในกลุ่ม Brassica oleracea หรือพวกบล็อกโคลี กระหล่ำดอก กระหล่ำปี คะน้า ฯลฯ พวกมันเลือกใช้อาวุธลับที่ชื่อว่า glucosinolate และ goitrogen เป็นด่านหน้าในการรับมือสิ่งมีชีวิตที่มากินมัน ซึ่งแน่นอนว่ารวมถึงมนุษย์ด้วย
สารพวกนี้เมื่อถูกเคี้ยว ถูกตัด หรือโดนความร้อน จะเปลี่ยนเป็นสารชื่อ isothiocyanate ซึ่งหลายงานวิจัยมองว่าสามารถกระตุ้นเอนไซม์ต้านอนุมูลอิสระในร่างกาย และลดความเสี่ยงมะเร็งได้ แต่ในขณะเดียวกัน... มันก็สามารถ “ยับยั้งการดูดซึมแร่ธาตุสำคัญ” อย่างไอโอดีน สังกะสี เหล็ก และแคลเซียมได้ด้วย โดยเฉพาะหากกินดิบ หรือกินปริมาณมากเป็นประจำ
ลองนึกภาพตามแบบขำๆ ว่า เรากินผักเพราะคิดว่ามันมีธาตุเหล็ก แต่ตัวมันเองกลับมี “แม่กุญแจเคมี” ที่ล็อกไม่ให้เหล็กดูดซึมได้จริง เหมือนพาเด็กไปสวนสนุกแล้วล็อกไว้ไม่ให้เล่นเครื่องเล่นอะไรเลย
นี่ยังไม่รวมถึง oxalate และ lectin ที่แฝงอยู่ในผักบางกลุ่ม ซึ่งสามารถจับกับแร่ธาตุจำพวกแคลเซียมหรือแมกนีเซียม และพาออกจากร่างกายไปทางลำไส้แบบไม่แยแสว่าเรากำลังขาดมันอยู่
คำถามคือ... แล้วคนที่กินสาย animal-based ซึ่งได้แร่ธาตุจากตับ ไข่แดง เนื้อแดงอยู่แล้ว จำเป็นต้องเสี่ยงกับผักที่มี anti-nutrient สูงแบบนี้ไหม?
คำตอบอาจจะไม่ได้ตรงไปตรงมาเหมือนสูตรยำปลากระป๋อง แต่ถ้าจะตอบในแนวระมัดระวังและตั้งอยู่บนหลักการชีววิทยา คือ “หากจะกินผักกลุ่มนี้ ควรกินในปริมาณที่พอดี และต้องผ่านการปรุงที่เหมาะสม” เช่น ลวก ต้ม หรือนึ่ง เพื่อสลายฤทธิ์ของสารเหล่านั้นลงไปให้ได้มากที่สุด
และที่สำคัญที่สุดอย่าเชื่อว่าผักมีแต่คุณเสมอไป เพราะในขณะที่แร่ธาตุจากเนื้อสัตว์มาพร้อมเอนไซม์ช่วยดูดซึมและไม่มีตัวขัดขวาง แร่ธาตุจากพืชกลับต้องฝ่าด่านสารยับยั้งมากมายที่ซ่อนอยู่
การกินแบบ animal base ที่เน้นเนื้อ เครื่องใน ไข่ น้ำมันดี และหลีกเลี่ยงน้ำตาล เป็นทางเลือกที่ทำให้ร่างกายได้รับสารอาหารสำคัญในรูปแบบที่ดูดซึมได้เต็มที่ ไม่ต้องพึ่งพาการเล่นปาหี่ของเคมีพืชที่คอยยับยั้งการดูดซึม เพราะสุดท้าย ถ้าเรามองอาหารเป็นเหมือนบทสนทนา ผักบางชนิดอาจจะพูดว่า “ฉันดีนะ กินฉันสิ” แต่ลึกๆ แล้ว มันกำลังพูดภาษาสารพิษที่เราแปลไม่ออก
แต่ทำความเข้าใจกันก่อนนะครับว่า เวลาเราพูดเรื่องนี้ไม่ใช่ว่า plant = toxic คือมันมีความพอดี มีกระบวนการบางอย่างที่เราต้องสกัดมันออกมาใช้งาน เหมือนไทยโบราณเรารู้ดีว่า พืช สมุนไพร ยา มันคือเส้นทางการใช้พืชจากความรู้ของมนุษย์ ดังนั้น มองพืชเป็น option ของสารพฤกษะ สารสำคัญ ได้นะครับ ไม่ต้องหัวสี่เหลี่ยมขนาดว่า เห้ย พืช กูไม่เอาเว้ย อะไรขนาดนั้นนะทิด
สารพฤกษะไม่ใช่วิตามิน ไม่ใช่แร่ธาตุ แต่เป็นสารที่พืชสร้างขึ้นเองเพื่อใช้ป้องกันตัวเองจากศัตรูพืช รังสี UV หรือเชื้อจุลินทรีย์ เรารู้จักชื่อพวกนี้อยู่ไม่น้อย เช่น
กลูโคซิโนเลต (glucosinolate) จากตระกูลกะหล่ำ ไลโคปีน (lycopene) จากมะเขือเทศ เรสเวอราทรอล (resveratrol) จากองุ่น ซาโปนิน (saponin) และ เลคติน (lectin) จากธัญพืชและถั่ว
สารพฤกษะมีหลายหมื่นชนิด และในบางกรณีมี ฤทธิ์ต้านอนุมูลอิสระ (antioxidant) หรือ ปรับภูมิคุ้มกัน จึงถูกจัดเป็นสารส่งเสริมสุขภาพ (nutraceutical) ได้ในบางมุม แต่ต้องระวัง... เพราะสารพฤกษะบางชนิดก็คือ "สารต้านสารอาหาร" (anti-nutrient) บางครั้งสิ่งที่เป็น “เกราะป้องกัน” ของพืช ก็กลายเป็น “กับดัก” สำหรับร่างกายเรา เช่น ไฟเตต (phytate) จับแร่ธาตุจำพวกเหล็ก สังกะสี ทำให้ร่างกายดูดซึมไม่ได้ ออกซาเลต (oxalate) สะสมในไตและอาจก่อให้เกิดนิ่ว กลูโคซิโนเลต ไปยับยั้งการดูดไอโอดีน ส่งผลต่อการทำงานของไทรอยด์ เลคติน ทำลายผนังลำไส้และกระตุ้นระบบภูมิคุ้มกันเกินจำเป็น
สารพฤกษะ คือ "ลูกเล่น" ทางชีววิทยาของพืช ที่อาจจะมีประโยชน์บ้าง ถ้าได้รับในปริมาณน้อย และในบริบทที่ร่างกายจัดการได้ แต่ถ้ามากเกิน หรือรับสะสมจากอาหาร plant-based ตลอดเวลา โดยไม่มีอาหารจากสัตว์มาคานสมดุล ก็อาจสร้างปัญหาเงียบๆ ระยะยาว
จะดีก็ฟงหวิน จะเลวก็ฟงหวิน พอเห็นภาพแล้วเนอะครับ
พรุ่งนี้เราจะขุดลงไปลึกอีกหน่อย กับเบื้องหลังของพืชพันธุ์ ที่ "เขา" บอกว่าทำเพื่ออาหารที่ดีของโลกครับ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ f3873798:24b3f2f3
2025-04-10 01:22:15
@ f3873798:24b3f2f3
2025-04-10 01:22:15O dorama O Lucro do Amor, disponível na Amazon Prime, oferece um ponto de partida para reflexões sobre as transformações culturais na Coreia do Sul, especialmente no que diz respeito à representação de relações afetivas e valores tradicionais. Enquanto analiso a obra, busco explorar como os arquétipos clássicos dos dramas coreanos — marcados por conservadorismo e estruturas patriarcais — estão sendo ressignificados sob a influência de movimentos sociais contemporâneos, como o feminismo e discussões globais sobre liberdade individual. A crítica central recai sobre a normalização de relacionamentos abertos e a relativização de promessas, temas que, embora raros na produção asiática, ecoam debates ocidentais.
Arquétipos Tradicionais e a Evolução dos Doramas
Historicamente, os doramas sul-coreanos consolidaram narrativas pautadas em dualidades rígidas: uma protagonista frágil, porém virtuosa (bondade, perseverança e sacrifício como marcas), e um protagonista masculino idealizado, detentor de poder intelectual ou social. Esses estereótipos refletiam valores confucionistas, nos quais a honra, o dever familiar e a estabilidade social eram pilares inegociáveis. A virtude feminina, por exemplo, era frequentemente associada à abnegação, enquanto o homem ocupava um papel de provedor e protetor.
A Ruptura em O Lucro do Amor
O drama em questão subverte parcialmente essa lógica. Se, por um lado, mantém a figura do "super-homem" — representado por Kim Ji Uk, carismático e resoluto —, por outro, introduz tensões modernas. A protagonista, em vez de se apoiar em ingenuidade, toma decisões pautadas em autonomia individual, ainda que isso implique romper compromissos afetivos. O conflito central gira em torno de sua escolha de se afastar de Ji Uk, justificada pela crença de que ele está com ela apenas por cumprir uma promessa feita à mãe da protagonista.
Aqui reside uma das contradições da trama: embora o personagem declare repetidamente seu amor genuíno, a protagonista insiste em invalidar seus sentimentos, reduzindo-os a um mero dever. Essa narrativa, embora pretenda valorizar a independência Ji Uk em não ficar preso em promessas, acaba por negligenciar a complexidade emocional dos personagens, tratando a quebra de promessas como um ato libertador, sem ponderar seu impacto ético. A mensagem que emerge — "sua vida, suas regras" — pode ser lida como um incentivo ao individualismo radical, em que compromissos são descartáveis em prol da autorrealização.
Relacionamentos Abertos e a Influência Cultural
O aspecto mais polêmico, contudo, é a introdução sutil de relacionamentos não monogâmicos. Dois personagens secundários adotam uma dinâmica aberta, retratada sem críticas ou consequências dramáticas significativas. Essa normalização, ainda que discreta, é emblemática de uma tendência global que vem permeando a produção midiática sul-coreana, tradicionalmente avessa a temas considerados tabus.
É importante contextualizar: a Coreia do Sul, apesar de sua indústria de manhwas e mangás explorar conteúdos considerados transgressores, mantinha nas novelas uma linha conservadora, reforçando família e matrimônio como instituições sagradas. A abertura a temas como poliamor ou fluididade de compromissos sugere uma assimilação de pautas progressistas, possivelmente influenciada por pressões internacionais e por movimentos locais que desafiam normas de gênero.
Crítica à Narrativa e Impacto Social
A fragilidade do dorama está na superficialidade com que aborda essas questões. A protagonista não enfrenta dilemas morais profundos; sua decisão parece motivada mais por uma rebeldia individualista do que por uma reflexão sobre autonomia versus responsabilidade afetiva. Ao romantizar a quebra de promessas como sinônimo de empoderamento, a trama banaliza a noção de honra — historicamente central na cultura coreana —, substituindo-a por uma ética utilitarista ("se não me serve, descarto").
Além disso, a representação de relacionamentos abertos carece de nuance. Enquanto no Ocidente tais dinâmicas são debatidas em camadas (desafios emocionais, ciúme, comunicação), aqui são apresentadas como meras escolhas lifestyle, desprovidas de conflito. Essa simplificação não apenas empobrece a narrativa, mas também serve como vetor de uma agenda ideológica que, para além do entretenimento, busca ressignificar valores sociais.
Entre a Inovação e a Desconstrução
O Lucro do Amor é um sintoma de uma Coreia do Sul em transição, onde tradição e modernidade colidem. Se, por um lado, é válido que as produções culturais reflitam a diversidade de pensamento, por outro, é preocupante a forma acrítica com que certos temas são inseridos, especialmente aqueles que minam a coesão social em nome de um individualismo pós-moderno.
A infiltração de pautas progressistas na mídia coreana não é neutra: assim como ocorreu no Ocidente, há riscos de que a erosão de instituições como a família e a promessa como pacto moral alimentem uma cultura de efemeridade e descompromisso. Enquanto espectadores, cabe questionar se essa "evolução" das narrativas realmente amplia o diálogo humano ou se, sob o disfarce de liberdade, nos empurra para uma sociedade cada vez mais fragmentada — onde o amor, longe de ser um lucro, torna-se uma transação descartável.
Nota Final:
O dorama, embora tecnicamente competente, falha em equilibrar inovação com profundidade. Serve mais como manifesto de uma agenda do que como obra que honre a complexidade das relações humanas — um alerta sobre os rumos da cultura pop globalizada. -
 @ c3e23eb5:03d7caa9
2025-04-10 00:41:12
@ c3e23eb5:03d7caa9
2025-04-10 00:41:12The issue I have with the term "mesh networks" is that it is associated with a flat network topology. While I love the idea of avoiding hierarchy, this simply doesn't scale.
Data Plane: How the Internet Scales
The internet on the scales because it has a tree like structure. As you can see in the diagram below, global (tier 1) ISPs branch out to national (tier 2) ISPs who in turn branch out to local (tier 3) ISPs. ``` ,-[ Tier 1 ISP (Global) ]─-───────[ Tier 1 ISP (Global) ] / |
/ ▼
[IXP (Global)]═══╦═══[IXP (Global)]
║
Tier 2 ISP (National)◄──────────╗
/ \ ║
▼ ▼ ║
[IXP (Regional)]════╬══[IXP (Regional)] ║
/ \ ║
▼ ▼ ║
Tier 3 ISP (Local) Tier 3 ISP (Local) ║
| | ║
▼ ▼ ▼
[User] [User] [Enterprise]▲ IXPs are physical switch fabrics - members peer directly ▲ Tier 1/2 ISPs provide transit through IXPs but don't control them ```
This structure also reflects in IP addresses, where regional traffic gets routed by regional tiers and global traffic keeps getting passed up through gateways till it reaches the root of the tree. The global ISP then routes the traffic into the correct branch so that it can trickle down to the destination IP at the bottom.
12.0.0.0/8 - Tier 1 manages routing (IANA-allocated) └─12.34.0.0/16 - Tier 2 allocated block (through RIR) └─12.34.56.0/24 - Tier 3 subnet via upstream provider ├─12.34.56.1 Public IP (CGNAT pool) └─192.168.1.1 Private IP (local NAT reuse)Balancing idealism with pragmatism
This approach to scaling is much less idealistic than a flat hierarchy, because it relies on an authority (IANA) to assign the IP ranges to ISPs through Regional Internet Registries (RIRs). Even if this authority wasn't required, the fact that many users rely on few Tier 1 ISPs means that the system is inherently susceptible to sabotage (see 2019 BGP leak incident).
Control Plane: the internet is still described as decentralised
The internet is still described as decentralised because there is a flat hierarchy between
tier 1ISPs at the root of the tree. ``` INTERNET CORE (Tier 1 ISPs)
AT&T (AS7018) <══════════> Deutsche Telekom (AS3320) ║ ╔════════════════════╗ ║ ║ ║ ║ ║ ╚══>║ NTT (AS2914) ║<══╝ ║ ║ ║ ║ ║ ║ ╚═══════> Lumen (AS3356) ║ ║ ╚════╩════════════> Telia (AS1299) ```
The border gateway protocol (BGP) is used to exchange routing information between autonomous systems (ISPs). Each autonomous system is a branch of the "internet tree" and each autonomous system advertises routes to downstream autonomous systems (branches). However, the autonomous systems at the root of the tree also maintain a record of their piers, so that they can forward traffic to the correct peer. Hence, the following is a more complete diagram of the internet:
INTERNET CORE (TIER 1 MESH) ╔══════════════╦═════════════╦════════╦═════════════╗ ║ ║ ║ ║ ║ AT&T (AS7018) <══╬══> Lumen (AS3356) <══╬══> NTT (AS2914) ║ ║ ║ ║ ║ ║ ║ ╚══> Telia (AS1299) <══╝ ║ ║ ╚═══════════════════════════════╝ ║ ║ ╚═> Deutsche Telekom (AS3320) <═╝ ║ TREE HIERARCHY BELOW - MESH ABOVE ║ ▼ [ Tier 1 ISP ]───────────────────┐ / | | / ▼ ▼ [IXP]═══╦═══[IXP] [IXP] ║ ║ ▼ ▼ Tier 2 ISP◄──────────╗ Tier 2 ISP◄───────╗ / \ ║ / \ ║ ▼ ▼ ║ ▼ ▼ ║ [IXP]═╦[IXP] ║ [IXP]═╦[IXP] ║ / \ ║ / \ ║ ▼ ▼ ▼ ▼ ▼ ▼ Tier 3 ISP User Tier 3 ISP EnterpriseSo its a mesh network - whats wrong with that?
In the example above, NTT can only send traffic to Deutsche Telekom via Lumen or AT&T. NTT relies on its peers to maintain a correct record of the IP range that they are responsible for, so that traffic that was intended for Deutsche Telekom doesn't end up in the wrong network. An intentional or even accidental error in an autonomous system's routing tables can be detrimental to the flow of traffic through the network.
Hence, mesh networks require: * Reliability: peers rely on each-other not to fail (e.g., 2019 AWS US-East-1 availability) * Trust: peers must be honest about address ranges (e.g., 2018 BGP hijacking incident) * Central planning: BGP traffic engineering determines which route a packet takes
Application Layer Innovations
Now that we have a rough overview of how the internet is broken, lets think about what can still be done. The flat hierarchy that we associate with mesh networks sounds beautiful, but it doesn't scale. However, the tree-like structure assumes that most participants in the network rely on an authority to give them an address or a range of addresses so that they can communicate.
Overlay networks
Fortunately all it takes to interact with someone on nostr is their public key. The recipients client will render your signed and/or encrypted event no matter how it reaches them. Whether your note reaches them over the internet, over some other network or via a carrier pigeon doesn't matter. nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr is working on a NIP for that and I'm sure he will share an explanation of how it works.
Bitcoin Instead of a Routing Algorithm
Now that we have digital bearer assets (e-cash), users can pay their internet gateway (TollGate) for access to the internet even though they are still offline. Once the TollGate has redeemed the e-cash, it gives the user access to the internet.
Frictionless Switching between ISPs (TollGates)
Legacy internet service providers use KYC money (fiat) to transfer the cost of the infrastructure to their users. However, this means that they are able to identify which packet belongs to which user. The KYC nature of their interaction with the users also makes it difficult for users to switch ISPs when service providers undercut each-other. Internet users who are on e-cash rails can hop between ISPs frictionlessly since they buy small amounts of data frequently in a granular manner.
Users that have access to independent competing TollGates can switch between them freely, so its impossible for any one TollGate to prevent a user from connecting to the internet. The only thing a TollGate can do is attract traffic by providing cheaper and/or faster internet access.
Anyone can arbitrage connectivity
Now that users have non KYC internet, there is nothing stopping them from reselling access to their internet connection. Anyone who has a WiFi router and access to a cheap internet connection can act as a range extender by re-selling access to that gateway for people who aren't able to connect directly.
Now the route that the traffic takes through the network is determined dynamically by the markets. The individual TollGate operators select their gateways and set their prices when they create a business model. The customers select the route that best meets their needs by selecting a gateway for their next purchase.
-
 @ 28635a6d:ee6f3a73
2025-04-10 00:21:52
@ 28635a6d:ee6f3a73
2025-04-10 00:21:52Over the past few years, The School of Bitcoin (TSOBTC) has built a reputation as a decentralised, open-source educational initiative dedicated to financial sovereignty and digital literacy. Our faculty, contributors, and global community have worked tirelessly to create resources that embody the Free and Open-Source Software (FOSS) ethos, ensuring that knowledge remains accessible to all.
As part of our commitment to maintaining an open and transparent model, we are excited to announce that The School of Bitcoin is officially migrating to Consensus21.School. This transition is not just a rebranding--it marks the consolidation of all our initiatives, projects, and educational resources under the Consensus21.School banner. The School of Bitcoin will no longer exist as a separate entity.
This move comes as a response to growing confusion between our initiative and another entity operating under the domain schoolofbitcoin (SOB), which has taken a direction that does not align with our open-source philosophy. To reaffirm our dedication to FOSS and community-driven education, we are bringing everything--our courses, programs, and collaborations--into a singular, more focused ecosystem at Consensus21.School.
What Does This Mean for Our Community?
Rest assured, all the valuable content, courses, and educational materials that have been developed under TSOBTC will remain available. We continue to embrace a value-for-value model, ensuring that learners can access resources while supporting the ecosystem in a way that aligns with their means and values.
By consolidating under Consensus21.School, we are doubling down on the principles of decentralisation, self-sovereignty, and permissionless learning. This transition includes all of our key initiatives, including V4V Open Lessons, the Decentralised Autonomous Education System (DAES), and our involvement with the Plan B Network.
Full Migration of DAES and Plan B Network Collaboration
As part of this transition, the Decentralised Autonomous Education System (DAES) is now officially part of Consensus21.School and is fully reflected in the Consensus21.School Whitepaper. DAES will continue to provide a platform for aspiring learners to submit their Bitcoin project ideas for potential funding and mentorship, with active engagement in our Stacker News /~Education territory and Signal chat for collaboration. We invite contributors to support our learner fund and help bring innovative ideas to fruition within this new ecosystem.
Additionally, our collaboration with the Plan B Network will now operate under Consensus21.School. Through this partnership, we will continue teaching using the Plan B Network's curriculum to provide high-quality Bitcoin education and strengthen local Bitcoin communities. This global initiative remains a core part of our mission, now fully integrated within Consensus21.School.
Looking Ahead
With Consensus21.School, we will continue innovating in peer-to-peer learning, integrating cutting-edge developments in Bitcoin, Nostr, and decentralised technologies. We encourage our community to stay engaged, contribute, and help us build an even stronger foundation for the future of open education.
This is more than just a domain change--it is the next evolution of our mission. The School of Bitcoin as an entity is now retired, and all our efforts, including DAES and the Plan B Network collaboration, will move forward exclusively under Consensus21.School. We invite educators, students, and enthusiasts to join us in shaping this next phase of open financial education.
The journey continues, and we are thrilled to embark on this new chapter together
-
 @ 554ab6fe:c6cbc27e
2025-04-09 23:22:16
@ 554ab6fe:c6cbc27e
2025-04-09 23:22:16We all live with our bodies every day, but do we truly experience them? Does this experience of the body have a broader consequence on our interpretation of life and our experience of well-being? The ability to experience the sensations of the body is known as interoception, and mindfulness meditation seems to be a powerful way of enhancing this ability. Enhanced interoception may not just result in a better understanding of the body, but may lead to a general increase in subjective well-being. Furthermore, it also may be indicative of a broader truth about how we can reach a more profound level of consciousness.
In a previous post, I began an exploration into possible reasons why those who meditate claim to achieve an altered form of consciousness. I mentioned that across enlightenment-related research, there is a common experience and interpretation of being one with everything during these altered or heightened states. I proposed that this interpretation of reality was achieved through an improved capability of the brain to process incoming information. The argument stems from the idea that the brain is constantly receiving signals from internal and external stimuli, trying to interpret those signals using previous experiences and predicted models (Seth, 2013). The interpretation created, in part, manifests itself as our conscious reality. I used an analogy of a calm pond to describe a possible consequence of this neuroscientific idea: imagine the brain as this pond, where incoming signals can be thought of as raindrops. When a single raindrop falls upon a pond, the ripples created are distinct. It is incredibly easy to determine how big the raindrop was, where it dropped, and came from, etc. However, if there is a massive rainstorm, then it is almost impossible to interpret all the intersecting ripples, and it is very hard to understand the “information” of each raindrop. This is analogous to how our brains work. The busier the incoming signals, the more difficult it is to interpret the reality of what is happening. This would also be true for the signals within the brain manifested by our thoughts and ruminations. Therefore, the calmer the pond/brain, the clearer and more accurate understanding of our world, and ourselves, is achieved. Meditation may be a method to achieve this heightened state of awareness. I find this idea profoundly interesting, and so my goal is to further explore this idea using scientific evidence as support.
To further explore and verify this idea, I felt it was important to research interoception. If this idea holds water, then it should be observed that meditation allows an individual to achieve a better understanding of incoming stimuli, both internal and external. In this post, I will explore the ability to interpret internal stimuli, which is known as interoception.
A quick note before I continue: As I began researching this topic, I found that the study of interoception was quite complex. The research is constantly evolving, and previous notions are quickly dismissed as the research progresses. Therefore, much of the research presented is speculative, and surely not indicative of definitive truth. Nothing you ever read is definitive of course, but I find that this is especially true here. Regardless, it will adequately depict the fascinating nature of our bodies and the processes involved in interpreting ourselves and reality, hopefully highlighting how important interoception is, and how poorly it is understood.
Understanding the Different Senses
To begin, an outline of our body’s senses is required. Classically speaking, the senses are defined as teloreception (vision and hearing), proprioception (limb position), exteroception (touch), chemoreception (smell and taste), and interoception (sensations from the internal organs)(A. D. Craig, 2002). In this classical definition, sensations of pain, temperature, and itches belonged to the family of touch/exteroception (A. D. Craig, 2002). Therefore, the line between the stimuli from the outside world is clearly defined and separated from the stimuli coming from inside the body. However, more recent findings suggest that temperature, pain, and itch are distinct from touch because they are associated with different neuronal pathways, and the experiences of these sensations seem to rely upon post-processing (A. D. Craig, 2002, 2003). In other words, the experience of these stimuli is more related to the mind than pure touch is. Additionally, interoception is also being redefined. The lamina I spinothalamocortical system is one of the major neuronal pathways that provide the brain with interoceptive signals (A. D. Craig, 2002, 2003). This nerve, across multiple studies, has been shown to not just send signals regarding the organs, but a sense of the condition of the entire body as well (A. D. Craig, 2002). Therefore, interoception encompasses the general feelings we have about the body’s state of being including, but not limited to, thirst, hunger, penile stimulation, exercise/exhaustion, and the condition of our organs such as bladder, stomach, etc. (A. D. B. Craig, 2009). To further complicate things, some researchers have attempted to distinguish between different aspects of interoception (Garfinkel et al., 2015):
• interoceptive accuracy – “Objective accuracy in detecting internal bodily sensations” • interoceptive sensibility – “Self-perceived dispositional tendency to be internally self-focused and interoceptively cognizant” • interoceptive awareness – “Metacognitive awareness of interoceptive accuracy”
Here, the ability to accurately detect signals and the subjective belief of one’s accuracy is differentiated. The interoceptive awareness evaluates if your subjective confidence in your ability to sense the signals coincides with the true ability. Therefore, the mind and our subjective evaluation of our signals are incredibly related to our perceived understanding. For this reason, the neuroscience of interoception should be explored, to gain a better understanding of how it works. The two brain areas that are involved in interoception and that will be discussed here are: the insula and the anterior cingulate cortex (ACC).
Insula
The insula is located deep within the cerebral cortex, and likely plays the most important role in interoception. The insula, especially the anterior portion of the insula, is thought to be involved in bodily and emotional awareness (Giuliani et al., 2011). It plays a major role in interoception and the sensations of internal physical states (Fox et al., 2014; Wolf E. Mehling et al., 2012). Not only is it integral to generating mental images of the internal state, but it is required for the motivation to make reactions based upon the interpretation, which subsequently affect the quality of life and survival (Craig, 2002). Consequentially, it plays a predictive role in awareness and decision-making (Craig, 2009). Therefore, falling in line with the idea that consciousness is the product of the predictive model generating nature of the brain to understanding and interpret incoming stimuli, the insula is thought to be a major seat of human consciousness and awareness of self-hood (Craig, 2009; Fox et al., 2014; Seth, 2013). Already, there is a clear connection between interoception, body awareness, and consciousness within the scientific literature.
Anterior Cingulate Cortex (ACC)
The other brain region heavily involved in interoception is the ACC. Where the insula largely is involved in the processing of the signal, the ACC is more involved with the response to the signal (Craig, 2002). In other words, the insula is related to the limbic sensory cortex, whereas the ACC is associated with the limbic motor cortex (Craig, 2002). Most recent studies have also shown that the ACC and insula are co-activated when a person experiences feelings (Craig, 2002, 2009). For example, both brain regions are involved in the sensation of the intensity and unpleasantness of pain (Grant et al., 2011). This provides further evidence that interoception is both a feeling and a motivation (Craig, 2009). Additionally, this enhances the argument that our interpretations and feelings from our internal environment are there for survival. It supports the idea that our brain is organized in a way that makes predictions, generates a conscious experience, that then elicits a reaction for the continuation of life.
Meditation and Interoception
Interoception involves more than just sensory information. It influences our feelings, and our understanding of our body, self, and the surrounding world. This understanding and experience of the self are seemingly influenced by the practice of meditation. Not only is this idea espoused in the east, but recent research has also indicated that increased mindfulness is correlated with increase interoceptive awareness (de Jong et al., 2016; Farb et al., 2010; Hanley et al., 2017). The exact mechanisms to how this occurs are still unclear. However, fMRI studies have shown that mindfulness meditation seems to increase activation in the insula (Farb et al., 2010). This may indicate that mindfulness promotes neurogenesis in areas that promote interoception. On that same note, the cognitive practices of mindfulness meditation may promote a mental framework that is helpful towards interoception. Mindfulness meditation involves orienting one’s attention to their immediate experience and becoming aware of all incoming stimuli with an open, curious, non-reactive, and non-judgmental interpretation (Bishop et al., 2004). This process helps generate a feeling of safety within the body, and the individual learns to interpret thoughts not as concrete objects of reality, but simply as thoughts that come and go within the mind. Researchers have found evidence to suggest that the non-reactivity obtained through meditation practice is closely linked to the ability to sustain attention towards bodily sensations (Hanley et al., 2017). This concept closely links to the idea that the calmer the mind is, the better the brain can process incoming information. This article brings forward evidence that the brain, with a calmer mind, can process interoceptive information better.
Consciousness
An interesting observation amongst interoceptive research is that an increase in interoceptive awareness is negatively correlated with emotional distress, hence an increase in subjective well-being is achieved (Hanley et al., 2017; W E Mehling et al., 2012). This is further supported by the observation that sadness is correlated with decreased activation of the insula and ACC, the brain regions involved in interoception (Farb et al., 2010). The relationship between the ability to be aware of the internal signals of the body and our mental well-being is very interesting. It suggests that not only does a calm mind generate a greater ability to understand the inner body, but it generates a more positive orientation to said experience. Additionally, it may be possible that this positive outlook spills over into other aspects of life beyond the interpretation of the self. Perhaps the calmer mind generates an accurate and positive outlook on all information received. This is perhaps why those who are expert meditators seem to be so peaceful, loving, and have a feeling of unity amongst everything.
The way we interpret information influences our experience of both ourselves and the world. Being aware of the body and its sensations in a non-judgmental way, creates a general sense of well-being. This may be indicative of a deeper philosophical idea: that the calmer the mind, the more capable the brain can interpret and understand information. This would not only provide a more accurate depiction of reality but provide a more profound understanding of it. Leading to a perspective of the world that is more positive, and potentially more oriented around the idea that we are all one. I cannot claim this is true. Nonetheless, it will be a concept that I will continue to explore. Regardless, it does seem to be the case that mindfulness meditation is capable of increasing interoception and therefore well-being. This being the case, I highly recommend that anyone interested in this topic incorporates mindfulness practice into their life. Reading and thinking about these ideas are all well and good, but to achieve full understanding, one must practice and experience it for themselves.
References
Bishop, S. R., Lau, M., Shapiro, S., Carlson, L., Anderson, N. D., Carmody, J., Segal, Z. v., Abbey, S., Speca, M., Velting, D., & Devins, G. (2004). Mindfulness: A Proposed Operational Definition. Clinical Psychology: Science and Practice, 11(3), 230–241. https://doi.org/10.1093/clipsy.bph077
Craig, A. D. (2002). How do you feel? Nature Review. https://doi.org/10.1177/1359105308095062
Craig, A. D. (2003). Interoception: The sense of the physiological condition of the body. Current Opinion in Neurobiology, 13(4), 500–505. https://doi.org/10.1016/S0959-4388(03)00090-4
Craig, A. D. (2009). How do you feel — now? The anterior insula and human awareness. 10(January).
de Jong, M., Lazar, S. W., Hug, K., Mehling, W. E., Hölzel, B. K., Sack, A. T., Peeters, F., Ashih, H., Mischoulon, D., & Gard, T. (2016). Effects of mindfulness-based cognitive therapy on body awareness in patients with chronic pain and comorbid depression. Frontiers in Psychology, 7(JUN). https://doi.org/10.3389/fpsyg.2016.00967
Farb, N. A. S., Anderson, A. K., Mayberg, H., Bean, J., McKeon, D., & Segal, Z. v. (2010). Minding One’s Emotions: Mindfulness Training Alters the Neural Expression of Sadness. Emotion, 10(1), 25–33. https://doi.org/10.1037/a0017151
Fox, K. C. R., Nijeboer, S., Dixon, M. L., Floman, J. L., Ellamil, M., Rumak, S. P., Sedlmeier, P., & Christoff, K. (2014). Is meditation associated with altered brain structure? A systematic review and meta-analysis of morphometric neuroimaging in meditation practitioners. Neuroscience and Biobehavioral Reviews, 43, 48–73. https://doi.org/10.1016/j.neubiorev.2014.03.016
Garfinkel, S. N., Seth, A. K., Barrett, A. B., Suzuki, K., & Critchley, H. D. (2015). Knowing your own heart: Distinguishing interoceptive accuracy from interoceptive awareness. Biological Psychology, 104, 65–74. https://doi.org/10.1016/j.biopsycho.2014.11.004
Giuliani, N. R., Drabant, E. M., Bhatnagar, R., & Gross, J. J. (2011). Emotion regulation and brain plasticity: Expressive suppression use predicts anterior insula volume. NeuroImage, 58(1), 10–15. https://doi.org/10.1016/J.NEUROIMAGE.2011.06.028
Grant, J. A., Courtemanche, J., & Rainville, P. (2011). A non-elaborative mental stance and decoupling of executive and pain-related cortices predicts low pain sensitivity in Zen meditators. Pain, 152(1), 150–156. https://doi.org/10.1016/j.pain.2010.10.006
Hanley, A. W., Mehling, W. E., & Garland, E. L. (2017). Holding the body in mind: Interoceptive awareness, dispositional mindfulness and psychological well-being. Journal of Psychosomatic Research, 99, 13–20. https://doi.org/10.1016/j.jpsychores.2017.05.014
Mehling, W E, Price, C., Daubenmier, J. J., Acree, M., & Bartmess, E. (2012). The Multidimensional Assessment of Interoceptive Awareness (MAIA). PLoS ONE, 7(11), 48230. https://doi.org/10.1371/journal.pone.0048230
Mehling, Wolf E., Price, C., Daubenmier, J. J., Acree, M., Bartmess, E., & Stewart, A. (2012). The Multidimensional Assessment of Interoceptive Awareness (MAIA). PLoS ONE, 7(11). https://doi.org/10.1371/journal.pone.0048230
Seth, A. K. (2013). Interoceptive inference, emotion, and the embodied self. Trends in Cognitive Sciences, 17(11), 565–573. https://doi.org/10.1016/j.tics.2013.09.007
-
 @ 3c389c8f:7a2eff7f
2025-04-09 22:57:18
@ 3c389c8f:7a2eff7f
2025-04-09 22:57:18Your nsec/private key is your key to controlling all that you do on Nostr. Every action you take is signed by this private key, validating that was you that generated that event, whether it be a note, a like, a list, or whatever else. Like a broken record, I have to state that it is irreplaceable. YOU own your identity and no one else. It is your responsibility to keep your nsec safe, but of course, you also want to be able to use all the different apps and clients available. To aid you in this process, a few different tools have been developed. Let's take a look at some that are more common and easy-to-use, where to use them, and for what.
The Browser Extension
This is probably the simplest and most straight forward form of private key manager available. There are many options to choose from, each compatible with various, commonly used browsers, including mobile browsers. Many provide the option to manage multiple keys for different profiles. Some are simply a signer while others may include other features. The concept is very simple. The extension holds your key and exposes it only only enough to sign an event. These extensions can be set to different levels of manual approval that you can control based on the level of convenience you seek. The ease and convenience does trade off a bit of security, as your private key will be exposed momentarily each time you create an event. It is up to you to choose whether this is appropriate for your use. For casual browsing and social media use, it is a fairly good and easy to use option. Nearly all Nostr apps and clients support signing with this method.
The Remote Signer
Often referred as a "bunker", Nostr remote signers hold your private key completely offline and communicating with clients. Clients send events to the signer to be signed, which then sends back the signed event for publishing. This bunker can be hosted on your own hardware or managed by a truested 3rd party. As long as the signer is online, it can communicate as needed. The signer generates a "bunker string" that is used to communicate. These may seem cumbersome to set up, as each client that you intend to use will need its own permissions. Once all of the pieces and permissions are in place, most of this activity will happen in the background. Bunkers allow for a lot of flexibility. The "bunker string" for a single app can be shared with other users who you may want to be able to make posts on your behalf. Multiple people can manage a social media profile, while the main owner of that identity maintains control of the nsec. These bunker strings can be revoked and replaced at any time. This signing method is growing in popularity and many clients already offer support for it.
The Native Android Signer
Currently, Amber is the only native app available to handle Nostr event signing. It is an incredible tool for managing your Nostr key on your mobile device. The signing flow is similar to remote signing, as described above, but it can communicate with both your Android native Nostr apps and web clients accessed through most mobile browsers, eliminating the need for a browser extension. A similar app is under development for iOS, but I don't use any of those devices, so covering that here will only happen via other's opinions at a later date.
NcryptSec
NcryptSec signing works by encrypting your nsec on a local device, unlocked by a password that you choose. Support for this method is very limited, as the encrypted private key stays on your device. If you intend to use Nostr through one device and few apps, this can be a very secure option, as long as you can remember your password, as it cannot be changed.
NFC and Hardware Signers
Some devices have been developed to store your nsec completely offline on a device or NFC chip, and some clients have added support for scanning/connecting to sign. I haven't personally tried any of these options, nor do I intend to promote the sale of any particular products. If you are interested in these techniques and devices, the information is not hard to find. The price of a devices varies, depending on your feature needs.
There are also DIY options that utilize existing hardware, if you are into that sort of thing.
Higher Security and Recoverability Options
Creating a scheme that allows for recovery of a lost key while maintaining the integrity of a unique identity is no easy task. The key must be fractured into shards, encrypted, and distributed across multiple servers in various locations, while you maintain a portion or portions of your own. These servers are run by trusted 3rd parties who will then sign events "with" you. Some include a scheme of running your own always online hardware to act as host for these shards. I fall short on the technical understanding of certain aspects of these processes, so I will spare you of my attempt to explain. As far as I know, there are a couple of methods underway that are worth paying attention to:
Frostr nostr:nevent1qvzqqqqqqypzqs3fcg0szqdtcway2ge7zahfwhafuecmkx9xwg4a7aexhgj5ghleqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcqyrh3r7uhytc4dywjggxz24277xgqtvcadvnjfks6fram7gjpev9nuentfht
Promenade nostr:nevent1qvzqqqqqqypzqwlsccluhy6xxsr6l9a9uhhxf75g85g8a709tprjcn4e42h053vaqydhwumn8ghj7un9d3shjtnhv4ehgetjde38gcewvdhk6tcprdmhxue69uhhyetvv9ujuam9wd6x2unwvf6xxtnrdakj7qpqqqq0dlpwxhw5l97yrcts2klhr9zqqpcmdfpaxm8r7hygykp630cq23ggph
For a List of signers, please visit this post .
-
 @ 3c389c8f:7a2eff7f
2025-04-09 22:54:31
@ 3c389c8f:7a2eff7f
2025-04-09 22:54:31Your nsec/private key is your key to controlling all that you do on Nostr. Every action you take is signed by this private key, validating that was you that generated that event, whether it be a note, a like, a list, or whatever else. Like a broken record, I have to state that it is irreplaceable. YOU own your identity and no one else. It is your responsibility to keep your nsec safe, but of course, you also want to be able to use all the different apps and clients available. To aid you in this process, a few different tools have been developed. Let's take a look at some that are more common and easy-to-use, where to use them, and for what.
The Browser Extension
This is probably the simplest and most straight forward form of private key manager available. There are many options to choose from, each compatible with various, commonly used browsers, including mobile browsers. Many provide the option to manage multiple keys for different profiles. Some are simply a signer while others may include other features. The concept is very simple. The extension holds your key and exposes it only only enough to sign an event. These extensions can be set to different levels of manual approval that you can control based on the level of convenience you seek. The ease and convenience does trade off a bit of security, as your private key will be exposed momentarily each time you create an event. It is up to you to choose whether this is appropriate for your use. For casual browsing and social media use, it is a fairly good and easy to use option. Nearly all Nostr apps and clients support signing with this method.
The Remote Signer
Often referred as a "bunker", Nostr remote signers hold your private key completely offline and communicating with clients. Clients send events to the signer to be signed, which then sends back the signed event for publishing. This bunker can be hosted on your own hardware or managed by a truested 3rd party. As long as the signer is online, it can communicate as needed. The signer generates a "bunker string" that is used to communicate. These may seem cumbersome to set up, as each client that you intend to use will need its own permissions. Once all of the pieces and permissions are in place, most of this activity will happen in the background. Bunkers allow for a lot of flexibility. The "bunker string" for a single app can be shared with other users who you may want to be able to make posts on your behalf. Multiple people can manage a social media profile, while the main owner of that identity maintains control of the nsec. These bunker strings can be revoked and replaced at any time. This signing method is growing in popularity and many clients already offer support for it.
The Native Android Signer
Currently, Amber is the only native app available to handle Nostr event signing. It is an incredible tool for managing your Nostr key on your mobile device. The signing flow is similar to remote signing, as described above, but it can communicate with both your Android native Nostr apps and web clients accessed through most mobile browsers, eliminating the need for a browser extension. A similar app is under development for iOS, but I don't use any of those devices, so covering that here will only happen via other's opinions at a later date.
NcryptSec
NcryptSec signing works by encrypting your nsec on a local device, unlocked by a password that you choose. Support for this method is very limited, as the encrypted private key stays on your device. If you intend to use Nostr through one device and few apps, this can be a very secure option, as long as you can remember your password, as it cannot be changed.
NFC and Hardware Signers
Some devices have been developed to store your nsec completely offline on a device or NFC chip, and some clients have added support for scanning/connecting to sign. I haven't personally tried any of these options, nor do I intend to promote the sale of any particular products. If you are interested in these techniques and devices, the information is not hard to find. The price of a devices varies, depending on your feature needs.
There are also DIY options that utilize existing hardware, if you are into that sort of thing.
Higher Security and Recoverability Options
Creating a scheme that allows for recovery of a lost key while maintaining the integrity of a unique identity is no easy task. The key must be fractured into shards, encrypted, and distributed across multiple servers in various locations, while you maintain a portion or portions of your own. These servers are run by trusted 3rd parties who will then sign events "with" you. Some include a scheme of running your own always online hardware to act as host for these shards. I fall short on the technical understanding of certain aspects of these processes, so I will spare you of my attempt to explain. As far as I know, there are a couple of methods underway that are worth paying attention to:
Frostr nevent1qvzqqqqqqypzqs3fcg0szqdtcway2ge7zahfwhafuecmkx9xwg4a7aexhgj5ghleqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcqyrh3r7uhytc4dywjggxz24277xgqtvcadvnjfks6fram7gjpev9nuentfht
Promenade nevent1qvzqqqqqqypzqwlsccluhy6xxsr6l9a9uhhxf75g85g8a709tprjcn4e42h053vaqydhwumn8ghj7un9d3shjtnhv4ehgetjde38gcewvdhk6tcprdmhxue69uhhyetvv9ujuam9wd6x2unwvf6xxtnrdakj7qpqqqq0dlpwxhw5l97yrcts2klhr9zqqpcmdfpaxm8r7hygykp630cq23ggph
For a List of signers, please visit this post .
-
 @ 3c389c8f:7a2eff7f
2025-04-09 22:53:27
@ 3c389c8f:7a2eff7f
2025-04-09 22:53:27Your nsec/private key is your key to controlling all that you do on Nostr. Every action you take is signed by this private key, validating that was you that generated that event, whether it be a note, a like, a list, or whatever else. Like a broken record, I have to state that it is irreplaceable. YOU own your identity and no one else. It is your responsibility to keep your nsec safe, but of course, you also want to be able to use all the different apps and clients available. To aid you in this process, a few different tools have been developed. Let's take a look at some that are more common and easy-to-use, where to use them, and for what.
The Browser Extension
This is probably the simplest and most straight forward form of private key manager available. There are many options to choose from, each compatible with various, commonly used browsers, including mobile browsers. Many provide the option to manage multiple keys for different profiles. Some are simply a signer while others may include other features. The concept is very simple. The extension holds your key and exposes it only only enough to sign an event. These extensions can be set to different levels of manual approval that you can control based on the level of convenience you seek. The ease and convenience does trade off a bit of security, as your private key will be exposed momentarily each time you create an event. It is up to you to choose whether this is appropriate for your use. For casual browsing and social media use, it is a fairly good and easy to use option. Nearly all Nostr apps and clients support signing with this method.
The Remote Signer
Often referred as a "bunker", Nostr remote signers hold your private key completely offline and communicating with clients. Clients send events to the signer to be signed, which then sends back the signed event for publishing. This bunker can be hosted on your own hardware or managed by a truested 3rd party. As long as the signer is online, it can communicate as needed. The signer generates a "bunker string" that is used to communicate. These may seem cumbersome to set up, as each client that you intend to use will need its own permissions. Once all of the pieces and permissions are in place, most of this activity will happen in the background. Bunkers allow for a lot of flexibility. The "bunker string" for a single app can be shared with other users who you may want to be able to make posts on your behalf. Multiple people can manage a social media profile, while the main owner of that identity maintains control of the nsec. These bunker strings can be revoked and replaced at any time. This signing method is growing in popularity and many clients already offer support for it.
The Native Android Signer
Currently, Amber is the only native app available to handle Nostr event signing. It is an incredible tool for managing your Nostr key on your mobile device. The signing flow is similar to remote signing, as described above, but it can communicate with both your Android native Nostr apps and web clients accessed through most mobile browsers, eliminating the need for a browser extension. A similar app is under development for iOS, but I don't use any of those devices, so covering that here will only happen via other's opinions at a later date.
NcryptSec
NcryptSec signing works by encrypting your nsec on a local device, unlocked by a password that you choose. Support for this method is very limited, as the encrypted private key stays on your device. If you intend to use Nostr through one device and few apps, this can be a very secure option, as long as you can remember your password, as it cannot be changed.
NFC and Hardware Signers
Some devices have been developed to store your nsec completely offline on a device or NFC chip, and some clients have added support for scanning/connecting to sign. I haven't personally tried any of these options, nor do I intend to promote the sale of any particular products. If you are interested in these techniques and devices, the information is not hard to find. The price of a devices varies, depending on your feature needs.
There are also DIY options that utilize existing hardware, if you are into that sort of thing.
Higher Security and Recoverability Options
Creating a scheme that allows for recovery of a lost key while maintaining the integrity of a unique identity is no easy task. The key must be fractured into shards, encrypted, and distributed across multiple servers in various locations, while you maintain a portion or portions of your own. These servers are run by trusted 3rd parties who will then sign events "with" you. Some include a scheme of running your own always online hardware to act as host for these shards. I fall short on the technical understanding of certain aspects of these processes, so I will spare you of my attempt to explain. As far as I know, there are a couple of methods underway that are worth paying attention to:
Frostr nevent1qvzqqqqqqypzqs3fcg0szqdtcway2ge7zahfwhafuecmkx9xwg4a7aexhgj5ghleqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcqyrh3r7uhytc4dywjggxz24277xgqtvcadvnjfks6fram7gjpev9nuentfht
Promenade nevent1qvzqqqqqqypzqwlsccluhy6xxsr6l9a9uhhxf75g85g8a709tprjcn4e42h053vaqydhwumn8ghj7un9d3shjtnhv4ehgetjde38gcewvdhk6tcprdmhxue69uhhyetvv9ujuam9wd6x2unwvf6xxtnrdakj7qpqqqq0dlpwxhw5l97yrcts2klhr9zqqpcmdfpaxm8r7hygykp630cq23ggph
For a List of signers, please visit this post .
-
 @ 3c389c8f:7a2eff7f
2025-04-09 22:40:45
@ 3c389c8f:7a2eff7f
2025-04-09 22:40:45You might see these terms used interchangeably throughout the Nostr network. Since Nostr is a decentralized protocol and not a platform, there is often a lack of consensus around particular terminologies. At times, it's important to differentiate between them, so that you can determine what is being stated. In the truest sense, there is no central entity to maintain a Nostr 'account' on your behalf, though some Nostr-based platforms may offer to do so. There's also no one to verify your 'identity'. This is something that you create, maintain and control. It is 100% yours. In a sense, you verify yourself through your interactions with others, with the network of clients and relays, and by protecting your nsec (secret key). A profile is generally considered to be a single place for displaying your content and any information about yourself that you've chosen to share, but its a little more complicated than that with Nostr. Let's take a closer look at all 3 terms:
Identity:
Your Nostr identity becomes yours from the moment you generate your key pair. The two parts each provide unique perspective and functionality. (Remember, there is no central entity to issue these key pairs. You can screw up and start over. You can maintain multiple key pairs for different purposes. If all of this is new and unfamiliar, start simply with the intention of trial and error.)
Half of the equation is your nsec. As long as you maintain control of that secret key, the identity is yours. You will use it to sign the notes and events that you create on Nostr. You will use it to access functionality of various tools and apps. You can use it to send monetary tips for content you find valuable. The reputation that you build through posting & interacting on Nostr will signal to others what type of person or profile this is, whether it's a genuine person, a bot (good or bad), a collection of works, etc. You might come across information that compares your nsec to a password. While a fair comparison, its important to remember that passwords can be reset, but your private key CANNOT. Lost access or control of your nsec means a loss of control over that identity. When you have decided to establish a more permanent identity, write it down, keep it safe, and use the appropriate security tools for interacting online.
The other half of this equation is your npub. This public key is used to find and display your notes and events to others. In short, your npub is how your identity is viewed by others and your nsec is how you control that identity.
Npub can also act a window into your world for whoever may choose to view it. As mentioned in a previous entry, npub login enables viewing Nostr's notes and other stuff in a read-only mode of any user's follow feed. Clients may or may not support this, some will even allow you to view and subscribe to these feeds while signed in as yourself via this function. It the basis of the metadata for your profile, too.
Profile:
Profile, in general, is a collection of things about you, which you have chosen to share. This might include your bio, chosen display name, other contact information, and a profile photo. Similar to traditional socials, veiwing Nostr profiles often includes a feed of the things you have posted and shared displayed as a single page. People will recognize you based on the aspects of your profile more than they will by your actual identity since an npub is a prefixed random string of characters . Your npub bridges a gap between strictly machine readable data and your human readable name, but it is not as simple as a name and picture. You will choose your photo and display name for your profile as you see fit, making you recognizable. These aspects are easy for copycat scammers to leverage, so your npub will help your friends and followers to verify that you are you, in the event that someone should try to copy your profile.
The Nostr protocol has another profile aspect that is important to know about, but as a general user, you shouldn't have to worry much about it. This is your nprofile. It combines your npub (or the machine readable hex verison of it) with hints to what relays you are using to publish your notes. This helps clients, crawlers, and relays find your stuff for your followers. You may notice nprofile when you share a profile link or used in other actions. When you update your relay list, your client will adjust your nprofile and send a new copy to the appropriate relays. If your believe that a client is not doing that correctly, you can visit metadata.nostr.com and manage it yourself.
Account:
Across Nostr, it is common to see the term 'account' used to refer to the combination of your identity and profile. It is a relatable term, though it may imply that some account issuer exists, but no one issues a Nostr account to you. You create and maintain it yourself.
There are situations where a traditional account will exist, such as with media servers, relay subscriptions, custodial wallet hosts, or NIP-05 providers. These things will almost always be paid services and storage that you choose to use. (Reminder: all of these things are possible to DIY with a little knowhow and an old computer)
What Is The Right Terminology?
There is no simple or correct answer here. Developers and writers will use whatever terms fit their scope and topic. Context will matter, so it's important to differentiate by that more than any actual term.
-
 @ 3c389c8f:7a2eff7f
2025-04-09 22:38:15
@ 3c389c8f:7a2eff7f
2025-04-09 22:38:15You might see these terms used interchangeably throughout the Nostr network. Since Nostr is a decentralized protocol and not a platform, there is often a lack of consensus around particular terminologies. At times, it's important to differentiate between them, so that you can determine what is being stated. In the truest sense, there is no central entity to maintain a Nostr 'account' on your behalf, though some Nostr-based platforms may offer to do so. There's also no one to verify your 'identity'. This is something that you create, maintain and control. It is 100% yours. In a sense, you verify yourself through your interactions with others, with the network of clients and relays, and by protecting your nsec (secret key). A profile is generally considered to be a single place for displaying your content and any information about yourself that you've chosen to share, but its a little more complicated than that with Nostr. Let's take a closer look at all 3 terms:
Identity:
Your Nostr identity becomes yours from the moment you generate your key pair. The two parts each provide unique perspective and functionality. (Remember, there is no central entity to issue these key pairs. You can screw up and start over. You can maintain multiple key pairs for different purposes. If all of this is new and unfamiliar, start simply with the intention of trial and error.)
Half of the equation is your nsec. As long as you maintain control of that secret key, the identity is yours. You will use it to sign the notes and events that you create on Nostr. You will use it to access functionality of various tools and apps. You can use it to send monetary tips for content you find valuable. The reputation that you build through posting & interacting on Nostr will signal to others what type of person or profile this is, whether it's a genuine person, a bot (good or bad), a collection of works, etc. You might come across information that compares your nsec to a password. While a fair comparison, its important to remember that passwords can be reset, but your private key CANNOT. Lost access or control of your nsec means a loss of control over that identity. When you have decided to establish a more permanent identity, write it down, keep it safe, and use the appropriate security tools for interacting online.
The other half of this equation is your npub. This public key is used to find and display your notes and events to others. In short, your npub is how your identity is viewed by others and your nsec is how you control that identity.
Npub can also act a window into your world for whoever may choose to view it. As mentioned in a previous entry, npub login enables viewing Nostr's notes and other stuff in a read-only mode of any user's follow feed. Clients may or may not support this, some will even allow you to view and subscribe to these feeds while signed in as yourself via this function. It the basis of the metadata for your profile, too.
Profile:
Profile, in general, is a collection of things about you, which you have chosen to share. This might include your bio, chosen display name, other contact information, and a profile photo. Similar to traditional socials, veiwing Nostr profiles often includes a feed of the things you have posted and shared displayed as a single page. People will recognize you based on the aspects of your profile more than they will by your actual identity since an npub is a prefixed random string of characters . Your npub bridges a gap between strictly machine readable data and your human readable name, but it is not as simple as a name and picture. You will choose your photo and display name for your profile as you see fit, making you recognizable. These aspects are easy for copycat scammers to leverage, so your npub will help your friends and followers to verify that you are you, in the event that someone should try to copy your profile.
The Nostr protocol has another profile aspect that is important to know about, but as a general user, you shouldn't have to worry much about it. This is your nprofile. It combines your npub (or the machine readable hex verison of it) with hints to what relays you are using to publish your notes. This helps clients, crawlers, and relays find your stuff for your followers. You may notice nprofile when you share a profile link or used in other actions. When you update your relay list, your client will adjust your nprofile and send a new copy to the appropriate relays. If your believe that a client is not doing that correctly, you can visit metadata.nostr.com and manage it yourself.
Account:
Across Nostr, it is common to see the term 'account' used to refer to the combination of your identity and profile. It is a relatable term, though it may imply that some account issuer exists, but no one issues a Nostr account to you. You create and maintain it yourself.
There are situations where a traditional account will exist, such as with media servers, relay subscriptions, custodial wallet hosts, or NIP-05 providers. These things will almost always be paid services and storage that you choose to use. (Reminder: all of these things are possible to DIY with a little knowhow and an old computer)
What Is The Right Terminology?
There is no simple or correct answer here. Developers and writers will use whatever terms fit their scope and topic. Context will matter, so it's important to differentiate by that more than any actual term.
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 7d33ba57:1b82db35
2025-04-09 21:01:07
@ 7d33ba57:1b82db35
2025-04-09 21:01:07Nestled along the Cassowary Coast in Far North Queensland, Mission Beach is a dreamy stretch of palm-fringed sand where the Great Barrier Reef meets the Wet Tropics rainforest. It's serene, scenic, and refreshingly uncrowded—a perfect escape if you’re chasing natural beauty, island vibes, and a bit of adventure.
🌟 Top Things to Do in Mission Beach
1️⃣ Walk the Endless Beach
- A stunning 14-kilometer stretch of golden sand
- Often you’ll feel like you have it all to yourself
- Lined with coconut palms and mountain backdrops—ideal for morning strolls or sunset walks
2️⃣ Dunk Island Adventures
- Just a 10-minute boat ride away, Dunk Island offers hiking trails, snorkeling, and tranquil beaches
- Go for a day trip or camp overnight for the real castaway feel
- You can kayak there if you're feeling adventurous 🚣♀️
3️⃣ Spot a Cassowary in the Wild
- Mission Beach is one of the best places to see the endangered cassowary, a striking and ancient-looking bird
- Keep your eyes peeled around Licuala Rainforest Walk or Bicentennial Trail
4️⃣ Skydiving with a Beach Landing 🪂
- One of the most iconic skydives in Australia
- Jump from 15,000 ft with views of the reef, rainforest, and islands—and land right on the sand!
5️⃣ Explore the Rainforest
- Walk in the Djiru National Park, home to lush jungle, creeks, and butterflies
- Or hike the Clump Mountain track for coastal views
🍉 Where to Eat & Chill
- The Garage Bar & Grill – Laid-back, good vibes, great burgers
- Baba Curry – Casual spot for Indian and tropical twists
- Mission Beach Tavern – Classic Aussie pub fare, cold beers, and often live music
- Spicy Thai Hut – Small, authentic, and big on flavor
🌺 Need-to-Know Tips
✅ Stinger season (Oct–May) means you should swim in designated netted areas or wear stinger suits
✅ Great base to explore the Atherton Tablelands, Tully Gorge, or Paronella Park
✅ Car rental is super handy—Mission Beach is spread out and public transport is limited
✅ It’s quiet here—perfect for relaxing, recharging, and going off-grid -
 @ 7d33ba57:1b82db35
2025-04-09 19:30:29
@ 7d33ba57:1b82db35
2025-04-09 19:30:29Havana (La Habana) is a city that grabs you with its vintage soul, vivid colors, and irresistible rhythm. Picture classic 1950s cars cruising past crumbling colonial mansions, locals dancing to live salsa in the streets, and the smell of strong Cuban coffee and cigars in the air. It’s not polished, but that’s part of the magic—Havana is alive.
🌟 Top Things to Do in Havana
1️⃣ Explore Old Havana (Habana Vieja)
- A UNESCO World Heritage Site with narrow streets, pastel facades, and grand plazas
- Must-see spots: Plaza Vieja, Plaza de la Catedral, Plaza de Armas, and El Capitolio
- Stop at a rooftop bar for mojitos and views over the city 🌆
2️⃣ Ride in a Classic American Car 🚗
- Take a guided tour in a vintage convertible—pink, red, or baby blue, your choice!
- Cruise along the Malecón, past the Hotel Nacional and through leafy neighborhoods like Vedado

3️⃣ Walk the Malecón
- Havana’s famous seaside promenade is the city’s open-air living room
- Best at sunset, when locals gather to fish, chat, play music, or just watch the waves crash
4️⃣ Visit the Museum of the Revolution
- Housed in Batista’s former palace, it tells the story of Cuba’s revolutionary history
- The building itself, with bullet holes and all, is part of the experience
5️⃣ Fábrica de Arte Cubano (FAC)
- A mix of gallery, nightclub, performance space, and bar
- Where Havana’s artsy and creative crowd hangs out—don’t miss it if you're into music or culture
🍹 What to Eat & Drink in Havana
- Ropa vieja – Shredded beef in tomato sauce, a Cuban classic
- Moros y Cristianos – Black beans and rice served with everything
- Tostones & yuca – Tasty fried plantains and cassava
- Mojitos & daiquiris – Best enjoyed where Hemingway drank them: La Bodeguita del Medio and El Floridita
- Cuban coffee – Small, strong, and sweet
🎵 Feel the Vibe
✅ Catch live music in every bar—from salsa and rumba to jazz and son cubano
✅ Watch a local dance show, or better yet, join a salsa class
✅ Visit Callejón de Hamel on Sundays for Afro-Cuban rhythms and street art🛺 Tips for Visiting Havana
🌞 Bring cash (euros or USD)—credit cards aren’t widely accepted
📶 Expect limited Wi-Fi—most people use Wi-Fi parks with pre-paid cards
💡 Embrace the slower pace—this is Cuba, not a rush
🚖 Use official taxis or pre-negotiate fares
💬 Learn a few Spanish basics—locals really appreciate it
💃 Talk to people—Cubans are warm, proud, and full of stories -
 @ 3c7dc2c5:805642a8
2025-04-09 19:29:48
@ 3c7dc2c5:805642a8
2025-04-09 19:29:48🧠Quote(s) of the week:
My current state of mind:
It is always the same story Government debases the currency and then blames business for profiteering and "the rich" who the Government has actually enriched. The root cause is government, and its addiction to printing money.
The DEBT crisis cannot be sustained. EU, UK, USA, China, etc., cannot continue the Ponzi scheme of printing more money to pay off old money. The previous rate for debt was 0.1%. Countries have to pay their Treasury Bonds, which will be around 4-5%. Wars start so they can all default, and then what comes after is a global financial reset. This is the information the majority of you do not understand or even look at.
Secretary of the Treasury of the United States, Scott Bessent, before the Election: “In the next few years, we are going to have some kind of grand economic reordering. Something equivalent to a new Bretton Woods. There’s a very good chance that happens in the next 4 years and I’d like to be a part of it.”
Any change of the Bretton Woods order will play in the cards of the scarce, politically neutral, immutable money: Bitcoin.
The problem has, and always will be the abuse and misuse of money by those in power. No one should ever have to work for a currency that others can print at will. The foundations are corrupted. Our money is broken.
This is the real problem.
Until that changes, nothing changes.
Educate yourself. Study Bitcoin.
🧡Bitcoin news🧡
On the 1st of April:
➡️The value of Metaplanet’s Bitcoin treasury is now 24x larger than the market cap of the company in April 2024.
On the 2nd of April:
➡️'Foundry just mined the emptiest non-empty block in over two years, containing only 7 transactions and weighing just 5369 units. The last block weighing less than this was by Binance Pool at height 769895 in January 2023 when the mempool was similarly empty, containing only 4 transactions and weighing 4370 units.' - Mononaut
➡️Last week I mentioned that Gamestop now has $ 1.48 billion available to purchase Bitcoin. If they invest that amount, $1.5 billion, in Bitcoin, it will make them the fourth largest Bitcoin holder among public corporations.
https://i.ibb.co/k6x0YLnV/Gne0shqb-QAAnx4-Z.jpg"
➡️Fidelity announces a no-fee Bitcoin retirement account that allows their 49 million customers to buy in Bitcoin.
➡️Publicly traded Enish announces to buy ¥100 million worth of Bitcoin.
➡️94.5% of the 21 million Bitcoin supply has been mined, based on its predictable predetermined issuance schedule—programmed in the protocol code, enforced by consensus, and verified through hundreds of thousands of globally distributed network nodes. Only 5.5% left to be mined over the next 115 years! - Wicked
➡️'Today, Breez launches Misty Breez, their latest application built using the Breez SDK. The Breez SDK was initially developed to simplify the process of integrating Lightning Network support into different consumer applications. Dozens of existing projects and companies currently build on Lightning using the SDK.
Breez: 'Lightning Made Easy → No channels. No setup fees. Just permissionless P2P payments.
Receive Offline Payments → Receive payments offline using mobile notifications.
Lightning Address Support → Accept payments with a customizable Lightning address.'Documentation for the Breez SDK Nodeless configuration used by Misty Breez is available here. The Github for the Misty Breez implementation is available here. Lastly, for users who wish to play around with the application, an early access release is available here for Android, and here for iOS. A direct APK download is available here.' - Bitcoin Magazine
➡️'Managing over 1.62 trillion dollars, the Bank of America CEO just said they would launch a stablecoin once it's legal. That amount of capital will disrupt all of crypto -- but, only a few networks will capture most of that value.' - Austin King
➡️'Bitcoin processed $5.5 trillion worth of transactions in Q1' - Pierre Rochard https://i.ibb.co/nqwkcCvn/Gni-MSFWYAAg7xu-1.png
On the 3rd of April:
➡️New Record Bitcoin Network Hashrate: 840,000,000,000,000,000,000x per second Bitcoin mining hashrate is rapidly approaching 1 zettahash.
➡️Metaplanet Inc. raised ~$17.8 million (¥2.63 billion) in equity capital through the first two days of April to further our Bitcoin Treasury Operations.
➡️Of 2024’s Top Performing Stocks, Only Two Remain Positive in 2025 — Both Are Bitcoin Treasury Firms. - METAPLANET - STRATEGY
➡️Finally, Jack Dorsey's Block enables Bitcoin payments on merchant terminals. "We are working on it" - Jack
➡️The Bitcoin Fear and Greed Index is now back at "Extreme Fear". Hodl the line people, hodl the line!
➡️'Today, the United States stock market lost $1.65 trillion. To help understand that number, it’s more than all Bitcoin combined. Not one coin—every coin. The global supply of Bitcoin is currently worth $1.63 trillion.' - Documenting Bitcoin
Just to give you one more perspective, the stock market has had the single worst day since the Covid crash. Bitcoin went as low as $3,843 during the Covid crash, and now it's $82,000. That is ~21x increase in just 5 years.
➡️Now, no matter what will happen with Bitcoin's price. Not enough people ask how much purchasing power $? will still hold by in the future. The nominal price is only part of the story.
https://i.ibb.co/qY2Rsfn0/Gno-Qu-Ki-WEAEp-EAM.jpg
On the 4th of April:
➡️Fortnite added a Bitcoin mine to the new map.
➡️Mastercard plans to help users send Bitcoin and cryptocurrency. "We've made a sizable bet on this," said Mastercard’s head of digital assets yesterday. The company has 3 billion cards worldwide and over 100 million places that accept them. So you are telling me that Mastercard wants to use a p2p cash system, Bitcoin, wild. Suddenly is becoming more suddenly all of a sudden. Hello, game theory!
➡️Bitdeer releases test footage of their new Bitcoin mining computer. The SealMiner A2 Pro Hyd calculates 500,000,000,000,000 hashes per second. That's some serious computing power. Do you wonder what the energy bill looks like...
https://www.asicminervalue.com/miners/bitdeer/sealminer-a2-pro-hyd
➡️Treasury Secretary Scott Bessent admits "Bitcoin is a store of value". In an interview with Tucker Carlson.
'Bessent was asked, "Why is Gold moving around the world right now?" After giving a one-line answer, he immediately of his own accord started saying "Bitcoin is becoming a store of value" This is quite the signpost for those with eyes to see.',
Ray Dalio was right, there's a change in world order. But it ain't China, it's Bitcoin.
➡️"Bitcoin is showing signs of breaking free from the gravitational pull of technology stocks during the financial market turmoil of the last few days." - Bloomberg
“We think Trump’s aggressive move has sped up a re-thinking of BTC’s longer-term value in a portfolio.” - Augustine Fan
https://i.ibb.co/cX1FLwr5/Gntq-Le-EXEAAZg-QA.jpg
On the 5th of April:
➡️The mysterious inventor of Bitcoin, going only by the username Satoshi Nakamoto, set April 5th—today—as their birthday. No one knows why for sure, but the date may be symbolic: it’s the same day the U.S. ordered citizens to turn in their gold under Executive Order.
➡️'A new Bitcoin Improvement Proposal (BIP) from developer Agustin Cruz suggests destroying unspent transaction outputs (UTXOs) to protect Bitcoin from potential quantum computer attacks. The proposal, “Quantum-Resistant Address Migration Protocol” (QRAMP), would require users to move funds to quantum-resistant wallets before a deadline or face their coins being effectively burned.' -Bitcoin News
This would mean that Satoshi either becomes active again or his/her Bitcoin is forever gone. There should never be a requirement to force move your coins. Try some other quantum-resistant approach.
Any quantum-resistant upgrade to the Bitcoin network should be a soft fork and completely optional. It is unethical to delete anyone's funds if they don't upgrade within an allotted time limit.
On the 6th of April:
➡️'Bitcoin mining difficulty recently adjusted upwards by 6.81% to an all-time high. Expect more small/medium operators to shut down as margins evaporate. Only survivors- those with ultra-cheap power or hobbyists who don't mine for profit. 'Bitcoin miners are the ultimate Bitcoin psychopaths. If you think we'll turn our miners off, you don't understand Bitcoin.' -Tomas Greif
On the 7th of April:
➡️ETH/BTC has fully retraced 5 years, now down 11% over that timeframe. This is catastrophic for the thesis that new cryptos “with more utility” can sustainably outperform the OG Bitcoin.
Willy Woo: 'ETH "ultrasound money" traded at $1569 today. It traded at $1448 in Jan 2018, thus a compounded IRR of 1.2% for a 7-year investment. I just thought I'd post this to help ETH holders as comments like these are what it takes to help an asset put in a bottom.'
➡️ Luke Broyles: '5 years ago we had a stock market crisis in 2020. Bitcoin fell 40% in one day and 65% in total. The S&P 500 fell 9.5% on that same day. Bitcoin bottomed at $4,000 then went up by 17x in the rebound from the crisis as we printed money.
If Bitcoin now falls 45% from the top and then goes up 10x in a similar timeframe, that would be a $600,000 Bitcoin in late 2026. I don’t care if Bitcoin is $50,000 or $600,000 next year. It is lower risk and more humanitarian than corporate paper.
Stocks had a higher human cost, less upside, and higher downside risk in time frames over 2 years. No matter what prices do I expect the S&P 500 to fall 80% against BTC in the next 5 years. I also suspect in 5 years $60,000 will sound as cheap as $4,000 and most will forget the pain of April 2025 like how most forgot March 2020.'
➡️ There are ~58 million millionaires in the world. And eventually, money printing will turn everyone into a millionaire. But there will only be 21 million bitcoin. 0.362 bitcoin per millionaire alive today. https://i.ibb.co/SDxYXYBz/Gn8-T-xc-XIAAc-GJM.png
➡️ Strategy discloses $5.91 billion in unrealized losses on its Bitcoin holdings for Q1 2025, according to a new SEC filing.
➡️ Cango increased its Bitcoin monthly production to 530.1 bitcoin in March, a 12% rise, with holdings reaching 2,474.8 BTC by month-end, up from 1,944.7 BTC in February. Deployed hashrate remained at 32 EH/s, with the average operating hashrate at 30.3 EH/s.
➡️'Bitcoin's MVRV for supply in loss drops to 0.88. This downturn is milder than previous major corrections in 2018 and 2022; investors remain cautiously optimistic rather than capitulating.' -Bitcoin News
💸Traditional Finance / Macro:
On February 20, JP Morgan CEO Jamie Dimon sold $234 million worth of JPM stock.
On February 22, Warren Buffett disclosed a record $334 billion cash balance. 30 trading days later, the Nasdaq 100 crashed -24%.
How did they know?
And just to show you how F'ed up the traditional markets are and acting like a memecoin:
On the 7th of April, the following sequence happened.
At 10:10 AM ET, rumors emerged that the White House was considering a "90-day tariff pause."
At 10:15 AM ET, CNBC reported that Trump is considering a 90-day pause on tariffs for ALL countries except for China.
By 10:18 AM ET, the S&P 500 had added over +$3 TRILLION in market cap from its low.
At 10:25 AM ET, reports emerged that the White House was "unaware" of Trump considering a 90-day pause.
At 10:26 AM ET, CNBC reported that the 90-day tariff pause headlines were incorrect.
At 10:34 AM ET, the White House officially called the tariff pause headlines "fake news."
By 10:40 AM ET, the S&P 500 erased -$2.5 TRILLION of market cap from its high, 22 minutes prior.
Never in history have we seen something like this.
Wall Street now trades like meme coins.
So basically > a guy reported fake news > all of World Finance aped the news and added 2.5T to the market > The news is fake, so everyone dumped so basically, finance is just memecoins with suits.
What a world we live in...
On the 2nd of April
👉🏽'President Trump just announced tariffs on 185 countries AT ONCE, one of the largest tariffs in US history. S&P 500 futures erased -$2 TRILLION of market cap in under 15 minutes.' ...'After 3+ years of compounding inflation: 2025 is the year when President Trump, Fed Chair Powell, and Treasury Secretary Bessent all came to the same conclusion. A recession is the only remaining way for inflation AND rates to fall.' -TKL
On the 3rd of April:
👉🏽How bad was today's stock market decline? Of the 11,406 trading days since January 1980, only 29 had larger declines.
https://i.ibb.co/3mg85KLt/Gno34klb-QAAJs52.png
The Magnificent 7 Index is now down over -30% from its all-time high seen on December 18th. While the S&P 500 is down -7.5% year-to-date, most investors are down much more. Large-cap tech is beyond bear market territory.
The Nasdaq 100 is in a bear market following a -6% drop today, the largest drop since March 2020. US stocks have now erased a massive -$11 TRILLION since February 19th with recession odds ABOVE 60%. The S&P 500 has lost ALL OF ITS RETURNS since March 2024.
Just to give you perspective. $10T, that’s a lot, right?
For context, the FED balance sheet is $6.7T. US M2 money supply $21.7T.Meanwhile, Bitcoin is up ~30% in the same period.
March 2020:
The S&P 500 is down 13% Bitcoin down
24% April 2025:
The S&P 500 is down 13% Bitcoin is down 5%
Another perspective, the S&P 500 dropping 10% in two days happened in:
October 1987
November 2008
March 2020
April 2025
On the 4th of April:
👉🏽Retail investors bought $4.7 billion in stocks yesterday, the most in a decade.
On the 5th of April:
👉🏽You can say whatever you wanna say about good ol' Warren Buffett, but he is killing it. https://i.ibb.co/NgfqjF50/Gnudptr-XQAAHPSW.jpg"
🏦Banks:
👉🏽 no news
🌎Macro/Geopolitics:
On the 1st of April:
👉🏽The scandal surrounding Le Pen. She is accused of fraud for allegedly using European Parliament staff for her French party. While everyone in Brussels knows this is exactly how things have worked for years. The whole system is full of these kinds of grey areas and conflicts of interest. Of course, it's not right, but it's also nearly impossible to prove definitively without political motivation. It's a political prosecution, whichever way you look at it. Now, I am no fan of Le Pen, not at all, but isn't it interesting that the unelected ECB President, Christine Lagarde, was accused of fraud, but without a criminal record—so she could become president of the ECB?
What scandal is Christine Lagarde known for, and what was the outcome?
Christine Lagarde was involved in a scandal known as the "Tapie affair" in France. This took place when she served as Minister of Economic Affairs and Finance from 2007 to 2011 under President Nicolas Sarkozy. The scandal revolves around an arbitration ruling in 2008, in which French businessman Bernard Tapie was awarded €403 million in damages in a dispute with the state-owned bank Crédit Lyonnais over the sale of Adidas in the 1990s. Lagarde approved the arbitration, which later became controversial as critics claimed the process was unfair and that Tapie—a known friend of Sarkozy—had been favored.
The outcome of the case came in December 2016, when Lagarde was found guilty of "negligence" by the Court of Justice of the Republic (CJR), a special tribunal for French government officials. The judge cited her “personality” and “international reputation,” as well as the context of the economic crisis during which she had to make decisions. Following the verdict, she remained in her position as managing director of the International Monetary Fund (IMF), which she had held since 2011, and in 2019 she was even appointed president of the European Central Bank (ECB), showing that the scandal did not significantly harm her career. However, the case remains a topic of debate, especially due to the perception of class-based justice and the large amount of taxpayer money involved in the payout.
And that is just one example. Just look up all the scandals around Ursula von der Leyen, president of the European Commission. And remember, unelected. Or our own Dutch EU playboy, Frans Timmermans. Today, the EU Commission publicly admitted that NGOs were paid to lobby Members of the European Parliament in favor of the Green Deal. https://www.eppgroup.eu/newsroom/commission-admits-financing-undue-lobbying-activities
'The European Commission admits it has used EU funds that were supposed to "fight climate change" for financing left-wing NGOs and climate organizations to silence the voices of European conservatives in a secretive influence operation. The funds came from the LIFE Program, which is supposed to fund environmental initiatives and has had a total budget of EUR 9 billion since 2014.'
https://x.com/visegrad24/status/1908561357114352127
Nearly a quarter of the 705 Members of the European Parliament have at some point been involved in a scandal or legal violation, reports Follow the Money. It concerns a wide range of behaviors, says investigative journalist Peter Teffer from FTM — from parking fines to corruption. "Perhaps the most extreme case is a Greek MEP who is currently doing his job from prison."
As mentioned before, it's a political prosecution whichever way you look at it. More and more, judicial systems in the West are being weaponized to crush the political opposition of the globalist elites / the ones that are in power now. Supposedly to save 'the rule of law'. Is it all just a coincidence—or a pattern of lawfare? Ask yourself that question.
I will give you a hint...It’s a tale of two justices: Le Pen faces potential jail time for allegedly misusing €2.9M in EU funds, while Christine Lagarde, found guilty of mismanaging €403M, walks free and now runs the European Central Bank!
Giorgia Meloni strongly criticized the disqualification of Marine Le Pen from the elections: “No one who truly believes in democracy can welcome a decision that targets the leader of a major party and deprives millions of citizens of their right to representation.”
Meloni’s right, banning opposition leaders isn’t democracy, it’s soft authoritarianism. Le Pen’s party earned 42% in the last presidential runoff. Silencing millions through legal tricks is a dangerous game.
For the Dutch readers: https://i.ibb.co/9HHsR3z3/Gnbuq-Pi-Xc-AAB1ye.jpg
We need a DOGE in Europe!
👉🏽'Job postings on Indeed dropped -10% year-over-year last week to the lowest in 4 years. Over the last 3 years, job postings have declined -33%. As a result, available vacancies are just 8% above pre-pandemic levels. Additionally, NEW job postings have dropped -40% since February 2022 to near the lowest since December 2020. Data provided by Indeed has been a leading indicator for the BLS-provided job openings data, suggesting more weakness ahead. The labor market is deteriorating.' -TKL
👉🏽'Despite a drop in unemployment and a rise in the labor force participation rate, the growing burden of retirees and public spending recipients is weighing on our finances and blocking essential reforms.' https://www.lepoint.fr/argent/comment-la-dependance-des-electeurs-a-l-argent-public-bloque-les-reformes-en-france-01-04-2025-2586277_29.php?at_variante=Community%20Management
30 million French citizens are economically dependent on public funds. That’s 44% of the population. 60% of eligible voters consist of civil servants, retirees, the unemployed, and welfare recipients. This is why France must reform — but cannot reform. For the Dutch readers, please click here for more insight: https://x.com/hollandgold/status/1908182490130341985
👉🏽The Top 1% of U.S. earners now have more wealth than the entire middle class.
On the 2nd of April:
👉🏽President Trump just announced tariffs on 185 countries AT ONCE, one of the largest tariffs in US history. As Luke Gromen mentioned last week: "Low tariffs on the world’s factories were part and parcel of the post-1971 structure of USD reserve status. Now that US tariffs are no longer low, the next shoe to drop will be a change to the post-1971 structure of USD reserve status."
UBS says a permanent implementation of President Trump's reciprocal tariffs would result in inflation rising to 5%. This would be a result of prices rising to "adjust to the higher costs of imports." We are on the verge of 5% inflation and negative GDP growth
'The rumor is that Trump is crashing the market so that The Fed cut the rate since several trillion of the national debt needs to be refinanced this year. When he refinances the debt on low rates he removes tariffs and the market moons.' -Bitcoin for Freedom
If true, that’s some 4D chess. The script would be: Get the 10-year down to sub 3.5, refinance the debt, initiate QE, roll back the tariffs, RF rate at 3.5% tech rips stocks up.
But I do find a problem with that theory. Most likely, tariffs will increase inflation, so there will be no QE. Trump is causing stagflation, which will kill jobs and businesses. The only people who benefit are oligarchs/the rich with extra cash to buy the dip.
👉🏽Almost every year since 08', GDP growth has been negative if you take out increases in government spending. You don't believe me:
https://i.ibb.co/8gLcnBT5/Gnke94-LWw-AAXHe-X.jpg"
Debt-fueled growth. Loosen monetary policy, FREE Money, ZIRP. Massive government spending has led to over 36T public debt with over $1T/yr. We have not fixed anything since 08. Just kicked the can down the road.
On the 3rd of April:
👉🏽Orthonormalist on Twitter cracked the tariff formula. It’s simply the nation’s trade deficit with the US divided by the nation’s exports to the US. Yes. Really. Vietnam: Exports 136.6, Imports 13.1 Deficit = 123.5 123.5/136.6 = 90% EU: exports 531.6, imports 333.4, deficit 198.2. 198.2/531.6 is 37, close to 39.
https://i.ibb.co/PG03LQwT/Gnmy-Krq-WQAAOf1-N.jpg
The fact that the Trump tariff rates are a simple calculation of the trade balance with that country means that the intention is to close the trade deficit, NOT negotiate for lower export tariffs. Seems the only way to avoid high tariffs is to improve the trade balance with the USA. Crude method, but ingenious all the same. Whether this approach is wise depends entirely on your economic priorities. Do you value balanced trade above all else, or do you prefer more nuanced economic efficiency and diplomatic stability?
Bottom line: simplistic, yes. Insane, no. Worth debating? Absolutely. Just some examples, the US administration imposed a 10% tariff on exports from Heard and McDonald Islands populated only by penguins. What a time to be alive.
https://i.ibb.co/DHdHRgSd/Gnm5-Eh-OXEAAy-GVc.jpg
I really love the Netflix series Peaky (focking) Blinders. The tiny island of St Pierre et Miquelon, featured in Peaky Blinders, St Pierre was a big warehouse for alcohol headed to the US, now got a 50% tariff because somebody bought 3.4 million worth of goods in July 2024 (most likely crustaceans). The 5,8k inhabitants "only" bought 100k worth of US goods in 2024. In the case of St Pierre, it's funny, but tragic in many others.
The tiny island of St Pierre et Miquelon got a 99% tariff because somebody bought 3.4 million worth of goods in July 2024 (most likely crustaceans) The 5,8 k inhabitants "only" bought 100k worth of US goods in 2024
Students for Liberty:
"It’s bold. It’s nationalist. It’s flawed. Because you can’t tariff your way to prosperity. And you can’t revive American industry without fixing what’s broken. The enemy isn’t foreign competition. It’s a big government. That’s what classical liberals have always warned: When the state manipulates markets, prints money, and micromanages trade, it always ends up hurting the very economy it claims to protect. Tariffs won’t save America. But freedom, competition, and reform might."
Trump and Bessent are orchestrating a grand economic reordering on US terms.
👉🏽President Trump invites President Bukele to the White House to discuss "ways we can support each other."
👉🏽China urges the US to "immediately" cancel reciprocal tariffs or they will take "counter-measures." Reciprocal tariffs on reciprocal tariffs should begin within the next 24 hours.
'China has three options: 1. Concede defeat to whatever terms Trump demands 2. Devalue the yuan by 20-40% 3. Unleash the biggest fiscal stimulus in its history (talking $2-3 trillion), which will push its debt off the chart' - ZeroHedge
I am not sure about that though. China isn’t collapsing—but it’s facing real structural headwinds: an aging population, a deflating housing bubble, rising youth unemployment, declining productivity, and global pushback.
Meanwhile, the U.S. still has deep capital markets, global alliances (well, let's see how the tariffs war will play out haha), energy independence, and innovation leadership.
So no—this is not “China checkmate.” It’s the start of a very long game.
👉🏽China claims that they found 2k+ TONNES of new Gold in the past 6 months that could reshape global markets. You can mine more gold if you want, but you can't mine more Bitcoin. That's the difference.
👉🏽That was quick: Thailand to Negotiate With the US on 36% Imposed Tariffs: PM Next: everyone else
👉🏽The European Union is preparing further countermeasures against newly announced US tariffs of 20%, per CNBC.
Apparently, no one is asking why, if these import tariffs are so harmful, the EU itself imposed high tariffs on imports for years. Tariffs that were actually higher than what the U.S. imposed on EU goods — which is what triggered the conflict in the first place.
On the 4th of April:
👉🏽The "World War 3" of Trade Wars Has Begun: Americans are waking up to the first MAJOR tariff retaliation against President Trump. China has announced 34% tariffs on ALL US goods with the S&P 500's 2-day losses now at -$3.5 TRILLION.
👉🏽'The last time the market dropped 9.5% in two days, the Fed unleashed a multi-trillion bailout of the economy including $500BN in QE, $1 trillion daily repo, and tens of billions in junk bond ETF purchases.' - ZeroHedge
👉🏽Treasury Secretary Scott Bessent tells Tucker Carlson - The top 10% of Americans own 88% of equities, and 88% of the stock market. The next 40% owns 12% of the stock market - The bottom 50% has debt - In the summer of 2024: more Americans were using food banks than they ever have in history
On the 5th of April:
👉🏽EU financed targeted campaigns against political opponents and uncomfortable voices.
👉🏽Germany considers withdrawing 1200 tons worth of gold from a US Federal Reserve vault following new tariffs.
👉🏽'On Thursday ALONE, hedge funds sold $40 BILLION of stocks in their largest daily selling spree since 2010. Short sales exceeded longs by 3 TIMES, with North American stocks accounting for 75% of volume.' -TKL
👉🏽'US job cut announcements spiked 205% year-over-year to 275,240 in March, the 3rd-highest monthly reading on record. This is also up 60% from the previous month when 172,017 cuts were announced. Moreover, this is higher than in any month during the 2008 Financial Crisis and the 2001 recession. Year-to-date, US employers have announced 497,052 job cuts, the highest quarterly total since Q1 2009. The US government has led all sectors with 216,215 cuts in March and 279,445 cuts year-to-date, up 672% from Q1 2024' -TKL
On the 7th of April:
👉🏽Hong Kong's stock market closes down 13.2%, the biggest one-day drop since 1997, and China's stock market officially opens with a -10% drop. China's stock market suffers worst single-day crash since 2008. And this isn't a meme coin, it's the Japanese stock market
https://i.ibb.co/7dqwPSc4/Gn5-Hjqc-Xw-AAzn-Yv.jpg
👉🏽European Commission president Ursula von der Leyen says the EU stands ready to negotiate a zero-for-zero tariff deal with the United States. Meanwhile, the President of the European Central Bank: The European Union wants to abandon the American credit cards Visa and Mastercard, PayPal, and Alipay. Make up your goddamnn minds ladies.
👉🏽If China invades Taiwan, the stock market gets cut in half. Apple, Nvidia, all of it. Conflict/trade issues would cause a global recession on top of it. It would make tariffs and Ukraine look like nothing. Immediate global disaster. Still the ultimate risk. Please read Ray Dalio's book The Changing World Order. When, not if...The fourth turning is real.
https://i.ibb.co/yFw7CkLg/Gnd6yqy-Ww-AAb-GFz.jpg
I am convinced this will happen because they need an excuse for why the market crashed or will crash in the future. The entire system in the USA and China is broken. No money, all fake, constant inflation, and debt.
War solves it for both, as mentioned in my quote at the start of this week's Weekly Recap.
I will end this week's Weekly Recap with the following quote made by Bitcoin Archive:
'Bitcoin is a neutral, global commodity without counterparty risk. Zero tariffs. The only commodity with a verifiably limited supply. 21 million forever. Your 0.01 BTC is the same quality as BlacRock's $50b.'
🎁If you have made it this far I would like to give you a little gift:
Start by taking 30 minutes to watch this video. Spend under 40 minutes of your time watching and showing you simply and compellingly what the problem is and the potential solution. Bitcoin.
https://www.satsvsfiat.com/en/#watch
After watching that video, I have another great video: https://youtu.be/k3NN_NZOdhY?si=xwBkv2lRHvEdCA0y
$13 trillion on war over the past two decades: Funded by inflation, hidden taxes, and silent theft. This is how fiat money became a weapon. In this episode with Lyn Alden: 'This might have been my top interview last year. In person at a conference in Madeira. Published today. An evergreen discussion on the Broken Money thesis. The history of monetary technology and its impacts on current socioeconomic realities.'
Credit: I have used multiple sources!
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly.
Use the code SE3997
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀
⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you?
If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-
 @ 16f1a010:31b1074b
2025-04-09 19:23:44
@ 16f1a010:31b1074b
2025-04-09 19:23:44
Arceus was born from nothing, not even chaos.



Arceus soon made Dialga, Palkia, and then Giratina. Dialga created time, Palkia created space, and Giratina created anti-matter. And thus, the Universe was born.Dialga, Palkia, and Giratina began battling and as a result were banished to their individual realms by Arceus.
Arceus then created Groudon, Kyogre, and Rayquaza. Groudon formed the huge celestial bodies known as planets, and the trio chose one to inhabit with life. Arceus created the sun, then shot off across the universe to create all the many stars.


But he had learnt from experience, so he tasked Rayquaza as the peace-keeper.

The trio set to work, with Groudon raising land violently, creating volcanoes and mountains; Kyogre, creating the seas, where the land was not, and Rayquaza making an atmosphere full of 'air'.
Sure enough, Kyogre's waters started to corrode Groudon's land, and this angered him. The two battled, but Rayquaza broke it up, and sent Groudon deep underground, while Kyogre was sent deep into the oceans, before returning out into the ozone layer.
Soon, Arceus returned, and it tried to make life, but failed miserably. So it created Regigigas. Regigigas moved the continents with its bare hands, piecing them together like a puzzle.

When the final chunk of land was put into place, the world sprung to life, with grass and trees sprouting everywhere. Finally, the world was ready for life.
Arceus sent Regigigas into a coma until it was needed once more. It then created thousands of Pokémon to inhabit the world. These Pokémon belonged to one of five races.
Celebi
 Jirachi
Jirachi  Mew
Mew 
Manaphy
 or Victini
or Victini 
It also created Latios and Latias, its personal agents, whom it sent flying through the universe in search of a species with great intelligence to live in harmony with its creations, before leaving once more to regain energy.


After much searching, Latias found an intelligent alien species known as Deoxys. They were bacterial but advanced. They chose a few of them and brought them back to their world.

For a while, things were fine, and the Deoxys and natives lived together in harmony. Until the Deoxys discovered they could 'infect' the natives and use their bodies. Suddenly, they were all infecting a host, and then war broke out.The Mew, Jirachi, Manaphy, Celebi, and Victini battled their infected brethren to set them free, while the Deoxys sought total dominance.
The war raged on for many centuries, until there were but a handful left of each species. Arceus returned and destroyed the last of the Deoxys, but the damage was done. The population of the world was little more than 20.
The Celebi retreated to the forests, hiding amongst the trees and in time. The Manaphy retreated to the sea, the Jirachi fell asleep, only waking up every so often, and the Victini hid in far-off lands.
This left only the Mew.During the war, three Mew had hidden under lakes in search of enlightenment.



Leaving only a handful of Mew left to roam. They were alone.The war had left the land in ruins; some places were battle-scarred beyond repair. Instead of lush grass, there were harsh deserts. This angered Groudon, sending him into a rage. Volcanoes spurted and spewed lava everywhere.
One day, a Mew was floating along when a sudden flow of lava approached it. Thinking quickly, Mew unleashed energy inside it that even Arceus didn't know about. It morphed the lava into a form and gave it LIFE. The first Heatran was created.

Arceus sensed this and had an idea. Gathering all the able Mew, it channeled immense power through them, using their life-giving abilities to create more living creatures. These were crude and unfinished, prototypes of what was to come.
Aerodactyl filled the sky, while Lileep, Cranidos, and Shieldon roamed the land.




Anorith, Omanyte, and Kabuto populated the seas.



Arceus also bestowed upon most of these beings the power to 'evolve' into more powerful creatures if the correct environment was met.
Finally, Latias returned once more. They had been far more thorough in their searching than before. However, Arceus had told them to stop, but guilt kept them going. They were determined to complete their job.
They brought humans from another planet. Basic but intelligent beings who definitely lacked the ability to infect anything. The humans settled in quickly, initially living relatively separately from the animals.
But Arceus wasn't convinced; he felt the need to test them.
First, Arceus created Articuno, who he ordered to send the planet into an Ice Age.

Articuno froze the planet, killing many creatures, but giving birth to new ones like Mamoswine.

To Arceus' pleasure, the humans adapted, creating structures out of ice and snow. The severe drop in temperature awoke Regigigas, who rose high above the land and saw what was happening.
The humans instantly fell in love with Regigigas, worshipping the titan and creating statues of it from ice. Touched by this, Regigigas found one of the statues and breathed life into it before returning to sleep.

However, this scared the humans, and they locked it away in a cave.
Realizing that the Ice Age did not affect the humans, Arceus created another bird, Moltres, and ordered it to send the world into a drought. The ice melted, and the water evaporated as the temperature rose higher and higher.

While the humans continued to adapt, using the skills they had learned with the ice and applying them to rock, the creatures weren't as lucky. The Mamoswine and other creatures that adapted to the cold died off, but new ones such as huge insects like Yanmega became common.

Once again, the drought awoke Regigigas, who once again saw a statue of himself. Thinking the humans would have learned from last time, Regigigas gave it life. But rumors of the living statue had been passed down and exaggerated since last time, and once again, the scared humans locked away this second 'Regi'.

When the drought finally wore off, Arceus began the third and final test. He created one more legendary bird, Zapdos. Zapdos created powerful electrical storms all across the land.

The storms killed off the last of the prototype creatures, leaving only the humans and the few pets they brought from their home land. One extremely intelligent man managed to harness the power of electricity, creating the first electronic device.
Of course, Regigigas awoke one final time. He discovered that the humans were far more evolved than expected, able to harness metals and electricity, albeit at a somewhat primitive level. More out of tradition than anything else, Regigigas created the third Regi out of steel. The humans were no longer scared of this Regi, but they sealed it away with the other two nonetheless, knowing that one day someone powerful enough would tame them.

Arceus was baffled. The humans had passed all three tests of harsh weather. Zapdos calmed the storms, and the world became peaceful once again.
Arceus herded the Mew together for a second time. Having learned the strengths and weaknesses of his prototype beings, Arceus was ready to go farther.
Siphoning its huge power through the small pink beings, Arceus filled the world with hundreds of species of creatures that would become known as 'Pokémon'. They were more diverse than it had ever imagined, filling the skies, land, and sea.
The life energies even reacted with the sun rays and moonlight, creating Ho-oh and Lugia respectively.


Some radiated out of the planet's moon, creating a population of Clefairy, as well as Cresselia on the light side and Darkrai on the dark side of the moon.



Lugia befriended the three elemental birds, and they followed him like a leader. Meanwhile, humans started to get closer to these new creatures, using them as slaves, weapons, or pets. The term 'Pokémon' arose from strange travelers and stuck.
The first Pokéballs were created from Apricorns, and the bond between human and Pokémon was complete.


Ho-oh took residence at the top of the Bell Tower. It was jealous of Lugia's trio of birds and wanted one of its own. One day, three Kimono girls entered its tower with a Jolteon, Flareon, and Vaporeon.



Ho-oh burnt down the tower with its Sacred Fire. Most escaped, but the three Pokémon were trapped and perished in the flames. Ho-oh soon resurrected them as Entei, Raikou, and Suicune.



Humans continued to evolve and take over the land, and Pokémon continued to work alongside and for them for many, many years.
That is the story of the Pokémon World.
-
 @ 378562cd:a6fc6773
2025-04-09 17:11:25
@ 378562cd:a6fc6773
2025-04-09 17:11:25So, this is the way I see things...
Bitcoin’s rise is not merely a technological revolution—it serves as a masterclass in game theory unfolding in real time. At its core, game theory examines how individuals make decisions when outcomes rely on the choices of others. Bitcoin adoption adheres to this model precisely.
Imagine a global network where each new participant increases the value and security of the system. Early adopters take a risk, hoping others will follow. The incentive to join grows stronger as more people opt in—whether out of curiosity, conviction, or FOMO. No one wants to be last to the party, especially if that party rewrites financial history.
Here’s how the game theory of adoption plays out:
-
🧠 First movers take risks but gain the most—they enter when the price is low and the potential is high.
-
👀 Everyone watches everyone else—people, companies, and countries are scanning the field for the next move.
-
The network effect kicks in—the more players are in the game, the more valuable and secure the system becomes.
-
⏳ Waiting can cost you—as adoption grows, the price of entry rises, making hesitation expensive.
-
No one wants to be left behind—especially in a global economy battling inflation and instability.
Game theory tells us that smart players make decisions that bring them the most goodies. As Bitcoin gets more popular, it’s like a party that’s really heating up, and you don’t want to be the one left outside! In this thrilling game, the early bird doesn’t just get the worm—it lands a juicy opportunity in a brand-new way to spend money. So don’t dawdle; now’s the time to jump in and grab your piece of this financial fiesta!
-
-
 @ 866e0139:6a9334e5
2025-04-09 16:36:35
@ 866e0139:6a9334e5
2025-04-09 16:36:35
Autor: Bewegung für Neutralität. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Der neue Schweizer Verteidigungsminister, Bundesrat Martin Pfister, wurde gewählt, weil er eine weitere Annäherung an die Nato und die Verteidigiungsstrukturen der EU befürwortet. Die «Bewegung für Neutralität» will ihm mit einem offenen Brief zeigen, dass die Basis anders denkt und die Neutralität hochhalten will. Wenn die Medien die Neutralität schon nicht vertreten, müssen wir es den Verantwortlichen selber sagen, in angemessener Deutlichkeit. Die Bewegung für Neutralität freut sich, wenn möglichst viele den offenen Brief unterzeichnen. (Text: Christoph Pfluger, Mit-Initiator).
Unter dem Titel «Hoffnungen, Sorgen und ein wachsamer Blick auf Ihre Arbeit» haben wir dem angehenden Bundesrat Martin Pfister einen offenen Brief geschrieben.\ \ Wir machen uns Sorgen, dass Druck auf ihn ausgeübt wird, sich der Nato weiter anzunähern und die Rüstungskosten der EU mitzutragen.\ \ Im Brief erinnern wir ihn an seinen Verfassungsauftrag (Art. 185), die Neutralität zu wahren und teilen ihm mit, dass seine Arbeit unter Beobachtung steht.\ \ Das Original des Briefes ist hier zu finden.

Herrn\ Martin Pfister\ 6319 Allenwinden\ \ 31. März 2025\ \ Hoffnungen, Sorgen und ein wachsamer Blick auf Ihre Arbeit\ \ Sehr geehrter Herr Bundesrat\ \ Wir möchten Sie ganz herzlich zu Ihrer Wahl in den Bundesrat beglückwünschen, ein Amt, das Sie dieser Tage antreten. Wir haben grosse Hoffnungen, dass Sie sich als Historiker der Wurzeln unseres Landes bewusst sind und sie durch Ihre Entscheidungen stärken. Die tragenden Werte der Eidgenossenschaft – Freiheit, Unabhängigkeit und direkte Demokratie – sind auch heute die Basis für eine Zukunft, die wir gerne den nächsten Generationen übergeben möchten.\ \ Alle diese Werte bauen auf der Neutralität. Denn wenn wir uns fremden Mächten und Militärbündnissen anschliessen oder auch nur «annähern», unterordnen wir uns Entscheidungen, die anderswo getroffen werden und irgendwelchen Interessen dienen. Wir verlieren damit nicht nur unsere Freiheit und unsere Unabhängigkeit, sondern auch das Primat des Souveräns und seiner direkt-demokratischen Instrumente.\ \ Wir hegen nicht nur Hoffnungen in Sie, wir haben auch Sorgen. Sie wurden gemäss allgemeiner Wahrnehmung mit den Stimmen derjenigen gewählt, die eine Öffnung gegenüber Allianzen anstreben und zu diesem Zweck die Neutralität «flexibilisieren», «aktualisieren» und «modernisieren» wollen.\ \ Wir halten diese «Flexibilisierung» für eine hochproblematische Position, die unser Land zu einer Parteinahme zwingt – und dies in einer Zeit, in der sich das bereits bestehende Kriegsgeschehen unvorhersehbar entwickelt und durchaus existenziell werden könnte.\ \ Die sichere Position in Konflikten Dritter ist die neutrale – nicht in schweigender, sondern in vermittelnder Haltung. Praktisch alle Kriege hätten durch frühzeitige Vermittlung durch eine neutrale Partei verhindert werden können.\ \ Eine Schweiz der guten Dienste muss deshalb neutral bleiben – nicht um Geschäfte zu machen, sondern um den Frieden zu gewinnen. Wir gehen davon aus, dass auch Sie das wollen.\ \ Wir befürchten aber auch, dass Druck auf Sie ausgeübt wird, nicht nur aus dem Parlament, sondern auch von fremden Kräften, die sich eine Beteiligung der Schweiz an Rüstungskosten wünschen oder sonstwie von einer kriegerischen Entwicklung profitieren. In vielen Ländern zählen Rüstungslobbies zu den verschwiegensten und mächtigsten Einflussgruppen.\ \ Wir hoffen, dass Sie diesem Druck standhalten, Ihrem Gewissen folgen und die Neutralität wahren, wie es gemäss Art. 185 der Bundesverfassung Ihr Auftrag als Bundesrat ist.\ \ Wir erlauben uns, Ihre Arbeit in diesem Sinn zu beobachten und Ihnen in angemessener Deutlichkeit mitzuteilen, wenn wir Ihren Verfassungsauftrag in Gefahr sehen.\ \ Wir wünschen Ihnen viel Weisheit und Erfolg in Ihrer grossen Aufgabe, die Ihnen das Schicksal so unerwartet gegeben hat und sichern Ihnen unsere Unterstützung bei der Wahrung der Neutralität zu. Wir wünschen uns eine Schweiz der guten Dienste und nicht der teuren Waffen.\ \ Mir vorzüglicher Hochachtung\ Der Vorstand der Bewegung für Neutralität:\ John C. Ermel\ Daniel Funk\ Alec Gagneux\ Dr. phil. Ariet Güttinger\ Peter König\ Christoph Pfluger\ Pia Rycroft\ Dr. phil. René Roca
u.v.m.
Hier kann der Brief unterzeichnet werden.
*«Die «Bewegung für Neutralität» wurde am 9. März 2025 als Verein gegründet. Er versteht sich als Trägerverein zur Unterstützung von lokalen Gruppen und Aktivisten, die sich für die Neutralität als Basis von Frieden, direkter Demokratie und eine Schweiz der guten Dienste einsetzen wollen. *
Die Friedenstaube fliegt auch in Ihr Postfach!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst an alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 51307ca1:de21c861
2025-04-09 16:02:59
@ 51307ca1:de21c861
2025-04-09 16:02:59{"type": "canvas_creation", "canvas_id": "canvas_1qqs7793", "timestamp": "2025-04-09T09:02:59.945647"}
-
 @ 51307ca1:de21c861
2025-04-09 15:46:25
@ 51307ca1:de21c861
2025-04-09 15:46:25{"type": "canvas_creation", "canvas_id": "canvas_c06fd5f6", "timestamp": "2025-04-09T08:46:25.204352"}
-
 @ 51307ca1:de21c861
2025-04-09 15:05:48
@ 51307ca1:de21c861
2025-04-09 15:05:48{"version": "1.0", "type": "canvas", "description": "This is a test canvas that will evolve with zaps", "initial_state": {"width": 1024, "height": 1024, "background_color": "#FFFFFF"}}
-
 @ 8d34bd24:414be32b
2025-04-09 14:45:28
@ 8d34bd24:414be32b
2025-04-09 14:45:28I was listening to “Ultimately with R.C. Sproul.” He made the comment that “Sin is so common that we don’t think it is that concerning, but it is especially concerning because it is so common.” This is so true.
I used to really look down on Adam and Eve for eating the forbidden fruit. I thought, “How hard is it to obey a single command? We have so many to obey today from God, government, parents, etc.” One day I finally realized two truths. Adam and Eve were adults, but they had not been around very long (the Bible doesn’t say how long, but the implication is not very long, maybe even as short as days after being created.) They didn’t have life experience. They also had never been lied to before. They weren’t looking at the world with suspicion. They lived in a perfect environment with a perfect, loving God. It would’ve never crossed their mind that a person would lie, so they trusted the lie instead of God.
Today, we live in a sinful, fallen world. Everyone lies. Everyone steals. Everyone is unkind. Everyone has selfish motives. Yes, there is a difference in how often and how “bad” the lie, the theft, the motive, or the unkindness, but sin is everywhere. We get used to it and it seems normal. When we act the same way, it doesn’t seem that bad. We just took a pen home from work, nobody will miss it. We just told the person what they wanted to hear, so we won’t hurt their feelings. It is only a little white lie. Yes, I was unkind, but that person really deserved it because they were worse. We think this way and excuse our sins because we aren’t as bad as someone else.
I’ve noticed as I’ve grown older that the age when you become old keeps getting older and older. Old is always a little bit older than I am. When I was 10, a teenager was really old. When I was 16, an 18 year old was an adult and old. When I was 20, a 40 year old was old. When I was 50, a 65 year old was old. Old keeps getting older because my reference is myself. The truth is that I am getting older. I am on the downhill slide. I am closer to death than I am to birth. My arbitrary, moving reference doesn’t change this fact.
In the same way, when we look at sin, we have the same problem. We are always looking for someone who sins worse to make us look better and to excuse our sins. We compare ourselves to sinful men instead of our perfect, holy, sinless Savior.
In an earlier post, I made the comparison of the lights in the sky. If you go outside on a dark, moonless night, you will see the stars in the sky shining. They seem bright, but some are brighter than others. You can compare the brightness of the stars and call some brighter and others darker, but when the sun rises, you can’t see any light from the stars. Their light is drowned out by the light of the sun. The sun is so much brighter that it is as if the stars don’t produce any light at all.
In the same way, we may do some good things. When we compare our good deeds to others, we may look better, but when the true reference, the Son of God is our reference, our good works look like they don’t exist at all. The differences between the best person and the worst person are insignificant, just like the brightness of the brightest star and the dimmest star seems insignificant when compared with the brightness of the Sun.
The cool thing is that there is another light in the sky, the moon. The moon doesn’t have any light of its own, but it is the second brightest light in the sky. Why? Because it reflects the light of the sun. We should be the same way. We will never measure up if we seek to be good and sinless. We will never meet the standard that Jesus set for us with His perfect, sinless, sacrificial life, but we can reflect the glory of Jesus in our lives.
Yes, when we sin, we can hurt others, but who are we really sinning against? David knows.
Be gracious to me, O God, according to Your lovingkindness;\ According to the greatness of Your compassion blot out my transgressions.\ Wash me thoroughly from my iniquity\ And cleanse me from my sin.\ For I know my transgressions,\ And my sin is ever before me.\ **Against You, You only, I have sinned\ And done what is evil in Your sight,\ So that You are justified when You speak\ And blameless when You judge.\ Behold, I was brought forth in iniquity,\ And in sin my mother conceived me.\ Behold, You desire truth in the innermost being,\ And in the hidden part You will make me know wisdom. (Psalm 51:1-6) {emphasis mine}
Yes, our sins can hurt other people and do, but the true damage is to the glory of our generous Creator God. We must confess our sins to God first and then to anyone we have hurt. We must accept that we deserve any judgement God gives us because He created us and everyone and everything with which we interact. Our allegiance, submission, and worship is due to our Creator God.
Because we can never fully understand how abhorrent sin is to God, I thought I’d share how a godly man, the priest and prophet, Ezra, reacted to sin among his brethren.
When I heard about this matter, I tore my garment and my robe, and pulled some of the hair from my head and my beard, and sat down appalled. Then everyone who trembled at the words of the God of Israel on account of the unfaithfulness of the exiles gathered to me, and I sat appalled until the evening offering.
But at the evening offering I arose from my humiliation, even with my garment and my robe torn, and I fell on my knees and stretched out my hands to the Lord my God; and I said, “O my God, I am ashamed and embarrassed to lift up my face to You, my God, for our iniquities have risen above our heads and our guilt has grown even to the heavens. Since the days of our fathers to this day we have been in great guilt, and on account of our iniquities we, our kings and our priests have been given into the hand of the kings of the lands, to the sword, to captivity and to plunder and to open shame, as it is this day. But now for a brief moment grace has been shown from the Lord our God, to leave us an escaped remnant and to give us a peg in His holy place, that our God may enlighten our eyes and grant us a little reviving in our bondage. (Ezra 9:3-8) {emphasis mine}
Ezra sees sin, shreds his clothes, pulls out his hair, and sits appalled. Do we feel even a fraction of the horror at guilt that Ezra showed? When faced with some Israelites marrying non-Israelite (many from the banned people groups), Ezra admits that “our iniquities have risen above our heads and our guilt has grown even to the heavens.” How many of us would think that was only a little sin or that since it was only a few people, it wasn’t that important? Ezra, instead of saying, “Why did you send us into exile for 70 years and why are you not blessing us now?” said, “But now for a brief moment grace has been shown from the Lord our God.” Instead of accusing God of not being good enough or kind enough, thanks God for His grace which was completely undeserved. If only we could look at sin in this way.
After all that has come upon us for our evil deeds and our great guilt, since You our God have requited us less than our iniquities deserve, and have given us an escaped remnant as this, (Ezra 9:13) {emphasis mine}
Ezra understood that we all deserve only judgment. Every good thing we receive is only due to God’s grace. Instead of asking why God would allow a bad thing to happen to us, we should be asking why God is so gracious to give us good things in our lives and not give us nothing but punishment.
Jesus also talked about our sins. Although it is good, when we are tempted to sin, to choose to not sin, even evil thoughts are sins. They mean our minds and hearts are not fully submitted to God.
“You have heard that the ancients were told, ‘You shall not commit murder’ and ‘Whoever commits murder shall be liable to the court.’ But I say to you that everyone who is angry with his brother shall be guilty before the court; and whoever says to his brother, ‘You good-for-nothing,’ shall be guilty before the supreme court; and whoever says, ‘You fool,’ shall be guilty enough to go into the fiery hell. Therefore if you are presenting your offering at the altar, and there remember that your brother has something against you, leave your offering there before the altar and go; first be reconciled to your brother, and then come and present your offering. Make friends quickly with your opponent at law while you are with him on the way, so that your opponent may not hand you over to the judge, and the judge to the officer, and you be thrown into prison. Truly I say to you, you will not come out of there until you have paid up the last cent.
“You have heard that it was said, ‘You shall not commit adultery’; but I say to you that everyone who looks at a woman with lust for her has already committed adultery with her in his heart. If your right eye makes you stumble, tear it out and throw it from you; for it is better for you to lose one of the parts of your body, than for your whole body to be thrown into hell. If your right hand makes you stumble, cut it off and throw it from you; for it is better for you to lose one of the parts of your body, than for your whole body to go into hell.
“It was said, ‘Whoever sends his wife away, let him give her a certificate of divorce’; but I say to you that everyone who divorces his wife, except for the reason of unchastity, makes her commit adultery; and whoever marries a divorced woman commits adultery.
“Again, you have heard that the ancients were told, ‘You shall not make false vows, but shall fulfill your vows to the Lord.’ But I say to you, make no oath at all, either by heaven, for it is the throne of God, or by the earth, for it is the footstool of His feet, or by Jerusalem, for it is the city of the great King. Nor shall you make an oath by your head, for you cannot make one hair white or black. But let your statement be, ‘Yes, yes’ or ‘No, no’; anything beyond these is of evil.
“You have heard that it was said, ‘An eye for an eye, and a tooth for a tooth.’ But I say to you, do not resist an evil person; but whoever slaps you on your right cheek, turn the other to him also. If anyone wants to sue you and take your shirt, let him have your coat also. Whoever forces you to go one mile, go with him two. Give to him who asks of you, and do not turn away from him who wants to borrow from you.
“You have heard that it was said, ‘You shall love your neighbor and hate your enemy.’ But I say to you, love your enemies and pray for those who persecute you, so that you may be sons of your Father who is in heaven; for He causes His sun to rise on the evil and the good, and sends rain on the righteous and the unrighteous. For if you love those who love you, what reward do you have? Do not even the tax collectors do the same? If you greet only your brothers, what more are you doing than others? Do not even the Gentiles do the same? Therefore you are to be perfect, as your heavenly Father is perfect. (Matthew 5:21-48) {emphasis mine}
Many people say that as New Testament believers, we are not under the Old Covenant and the Old Testament laws do not apply to us. While that may be true of the ceremonial laws, the truth is that Jesus made the laws stricter. It is still true that we are not to commit murder, but we are also not to hate another. It is still true that we are not to commit adultery, but we are also not to lust after another. We are also not to fight against those who mistreat us and we are to love those who hate us. Jesus expects more, not less, maybe because we now have the guidance and power of the Holy Spirit within us.
If we have the mind of Christ, we should despise the things God hates. If we have the heart of Christ, we should love even those who hate us and we should seek their eternal good. We should see with the eyes of Christ and see the hurt behind the hate and dishonesty. How do we do this? We need to fill our minds with the word of God. We need to obey Paul’s command to those in Philippi:
Finally, brethren, whatever is true, whatever is honorable, whatever is right, whatever is pure, whatever is lovely, whatever is of good repute, if there is any excellence and if anything worthy of praise, dwell on these things. (Philippians 4:8)
We need to so fill our mind with God’s word that God’s goodness overflows into our lives.
God of heaven, please change our hearts and minds and make them fully aligned with your heart and mind. Help us to see sin as you see sin and to see people as you see people. Help us to see the hurt instead of the lashing out, so we can have a merciful heart towards those who are unkind to us. Help us to fill our minds with your goodness and your word, so there is no room for evil in us. Make us more like you.
Trust Jesus
FYI, there are many people who can’t see their own sin and who discount the severity of sin. I am writing for these people. There are also people who have no trouble seeing their own sin. Their problem is not accepting the forgiveness of God. Never doubt that God has forgiven you if you have confessed your sins and trusted Jesus as Savior. Jesus has covered your sins and the Father sees only the holiness of Jesus. Your relationship with the Godhead is fully reconciled. You should do right out of thankfulness and love of God, but there is nothing else you need to do to be saved and have a right relationship with God.
-
 @ 0f9da413:01bd07d7
2025-04-09 14:23:54
@ 0f9da413:01bd07d7
2025-04-09 14:23:54 หลังจากที่เดินทางเกือบ 18 ชั่วโมงเราก็มาถึงหาดใหญ่กันแล้ว ช่วงระยะเวลาที่อยู่บนรถไฟเป็นอะไรที่เรี่ยเปี่ยมากๆ นั่งมองข้างทางส่วนมีเหตุการณ์อะไรนั่น ติดตามบทความพิเศษได้เร็วๆ นี้ ผมก็ได้พบเจอเพื่อนบน nostr ท่านหนึ่งที่อยู่หาดใหญ่อาสาพาทัวร์ในหาดใหญ่แห่งนี้ กัปตันนั่นเอง ขนาดชื่อเล่นจริงๆ ยังไม่เคยถามหลังจากที่ดูใน btcmap แล้วพบว่าร้านเปิดตอนกลางคืน ซึ่งเรามีเวลาคืนเดียวในการอยู่ที่หาดใหญ่ ดังนั้นหลังจากช่วงกลางวันพาทัวร์แถวสงขลากันแล้ว ก็ได้พากลับมาตามล่าหาร้านรับ bitcoin lighting ในหาดใหญ่ มีอยู่สามสถานที่ แต่มีเพียงสองร้าน คือ
หลังจากที่เดินทางเกือบ 18 ชั่วโมงเราก็มาถึงหาดใหญ่กันแล้ว ช่วงระยะเวลาที่อยู่บนรถไฟเป็นอะไรที่เรี่ยเปี่ยมากๆ นั่งมองข้างทางส่วนมีเหตุการณ์อะไรนั่น ติดตามบทความพิเศษได้เร็วๆ นี้ ผมก็ได้พบเจอเพื่อนบน nostr ท่านหนึ่งที่อยู่หาดใหญ่อาสาพาทัวร์ในหาดใหญ่แห่งนี้ กัปตันนั่นเอง ขนาดชื่อเล่นจริงๆ ยังไม่เคยถามหลังจากที่ดูใน btcmap แล้วพบว่าร้านเปิดตอนกลางคืน ซึ่งเรามีเวลาคืนเดียวในการอยู่ที่หาดใหญ่ ดังนั้นหลังจากช่วงกลางวันพาทัวร์แถวสงขลากันแล้ว ก็ได้พากลับมาตามล่าหาร้านรับ bitcoin lighting ในหาดใหญ่ มีอยู่สามสถานที่ แต่มีเพียงสองร้าน คือ
Soymilk Toyou ฉือฉาง และ น้ำเต้าหู้ SOYMILK TOYOU

น้ำเต้าหูหลากหลายรสชาติ มีอยู่สองสาขาอยู่บริเวณ ตลาดโต้รุ่งฉื่อฉาง และ ถนนปุณณกัณฑ์ สาขาแรกอยู่ในตลาดโต้รุ่ง ร้านเล็กๆ เหมาะกับการชื้อกลับ และอีกร้านหนึ่งอยู่บริเวณเป็นร้านที่เหมาะกับนั่งทานที่ร้าน ซึ่งมีเต้าหู้หลากหลายรสชาติ ให้เลือกจนตาลายกันเลยทีเดียว สำหรับสาขา ถนนปุณณภัณฑ์นั้นมีเมนูเพิ่มเติมอย่าง เฉาก๋วยนมสด พุดติ้ง เต้าถึง และเฉาก๊วยโบราณ สาขานี้ลักษณะร้านออกแนวเกาหลีหน่อยๆ ซึ่งก็ค่อนข้างเหมาะกับชื่อร้านเหมือนกัน ค่อนข้างได้ฟิลพอสมควร ซึ่งผมเองกับกัปตันเองก็ได้แวะทั้งสองร้าน 4 แก้ว น่าจะเป็นเบาหวานเร็วๆ นี้ แต่ยังมีอีกหลากหลายอย่างที่ผมยังไม่ได้ลองชิม คราวหน้าอาจจะต้องได้ไปแวะใช้บริการอีกครั้ง ทั้งสองสาขานี้มีป้ายรับ bitcoin lighting ด้วยซึ่งอาจจะต้องสังเกตกันนิดหนึ่ง หากต้องการใช้งาน ซึ่งทั้งสองร้านนี้ก็สปีนประมาณ 5,820 sats
Soymilk Toyou ฉือฉาง (ตลาดโต้รุ่งฉื่อฉาง)
 Google-map: https://maps.app.goo.gl/1PUVX3wkuzLBrQjw7
Google-map: https://maps.app.goo.gl/1PUVX3wkuzLBrQjw7BTC-map: https://btcmap.org/merchant/node:12351330907
น้ำเต้าหู้ SOYMILK TOYOU (ถนนปุณณกัณฑ์)
 Google-map: https://maps.app.goo.gl/FFaZSXKEvGwKvrwZ7
Google-map: https://maps.app.goo.gl/FFaZSXKEvGwKvrwZ7BTC-map: https://btcmap.org/merchant/node:12346018233
และเมื่อผมและกัปตันต้อง spin sats ทั้งสองร้านก็กลายเป็นว่าได้น้ำตาลมาหน่อยๆ แต่ไหนๆก็มาแล้วจะไม่ใช้ก็อย่างไรอยู่ ซึ่งรสชาติก็แตกต่างกันไปตามที่เราได้สั่ง ส่วนตัวเองสาขาตลาดโต้รุ่งฉื่อฉาง ผมสั่งน้ำเต้าหู้ธรรมดา และสาขา ถนนปุณณกัณฑ์ ก็น้ำลำใยบวกกับพุดติ้งเมนูของร้าน น้ำตาลน่าจะสไปรท์กันสุดๆแล้วละ 555+

ดูด(Dude) หลังจากเมากับความหวานทั้งสองสาขากันไปแล้ว เอ้ยนี่เราจะลุยกันต่อเรอะ เออว่ะ ก็กูนอนที่หาดใหญ่แค่คืนเดียวแล้วดันก็เปิดแค่กลางคืนด้วย ก็คงต้องอัดหน้าท้องแล้วละ กับอีกร้านหนึ่งที่รับ sats กับร้าน ดูด(Dude)
 หากดูในแผนที่อยู่ระหว่างกลางร้านก่อนหน้าทั้งสองสาขา กึ่งกลางพอดิบพอดี ร้านนี้เป็นร้านขายเครื่องดื่มและกับแกล้มและมีกับข้าวช่วงเย็น เป็นบาร์กลางคืน ไม่มีเบียร์เหล้าขายนะ (ในใจนึกว่าจะมีเสียอีก) แต่หากอยากจ่าย lighting อาจจะต้องแจ้งกับเจ้าของร้านหน่อยเพราะไม่เจอป้ายรับ lighting เราก็อัดน้ำถังไปอีกคนละแก้ว (แก้วถังที่ใส่น้ำแข็งเยอะๆ) นั่งคุยกันเพลินๆ ซึ่งทั้งสามร้านเราก็เมากับน้ำหวาน มีกับแกล้มซึ่งกินไม่ค่อยไหวแล้วเพราะไปเปย์สาวๆตอนเย็นไปแล้ว เอ้ย และร้านท้ายนี้หมดไปทั้งหมด 6,809 sats
หากดูในแผนที่อยู่ระหว่างกลางร้านก่อนหน้าทั้งสองสาขา กึ่งกลางพอดิบพอดี ร้านนี้เป็นร้านขายเครื่องดื่มและกับแกล้มและมีกับข้าวช่วงเย็น เป็นบาร์กลางคืน ไม่มีเบียร์เหล้าขายนะ (ในใจนึกว่าจะมีเสียอีก) แต่หากอยากจ่าย lighting อาจจะต้องแจ้งกับเจ้าของร้านหน่อยเพราะไม่เจอป้ายรับ lighting เราก็อัดน้ำถังไปอีกคนละแก้ว (แก้วถังที่ใส่น้ำแข็งเยอะๆ) นั่งคุยกันเพลินๆ ซึ่งทั้งสามร้านเราก็เมากับน้ำหวาน มีกับแกล้มซึ่งกินไม่ค่อยไหวแล้วเพราะไปเปย์สาวๆตอนเย็นไปแล้ว เอ้ย และร้านท้ายนี้หมดไปทั้งหมด 6,809 sats 
 Google-map: https://maps.app.goo.gl/41Tsj4GLWvm7M6TC6
Google-map: https://maps.app.goo.gl/41Tsj4GLWvm7M6TC6BTC-map: https://btcmap.org/merchant/node:12478715046
จบกันแล้วสำหรับสองร้านในหาดใหญ่ ตามบน BTC-map ถือว่าเราได้ไปครบแล้วในหาดใหญ่ ซึ่งโซนบริเวณภาคใต้นี่เป็นสถานที่ที่ผมซึ่งเป็นคนเหนือเองอยากจะได้เยี่ยมชมแวะไปหาและอยากไปเรียนรู้เกี่ยวกับวัฒนธรรมที่นี้ มันมีอะไรที่ผมอยากจะค้นหาและตามลิ้มลองรสชาติของอาหารปักใต้ แน่นอนยังมีอีกหลายสถานที่ที่กำลังจะมีให้ใช้งานในอนาคต ร้านค้าที่เกี่ยวข้องที่รับ lighting ซึ่งพอมีเยอะๆแล้วก็คงตามไล่ไปแวะชิมก็น่าจะไม่หมดแน่นอน อย่างน้อยๆ ผมเองก็ได้แวะไปเที่ยวหาเพื่อนที่อยู่บน nostr ที่นั่นที่นี้ แม้จะระยะเวลาสั้นๆ แต่ก็ถือว่าเป็นครั้งแรกที่ได้แวะเที่ยวหาดใหญ่ เที่ยวสงขลา ถ่ายรูปกับรูปนางเงือกหาดสมิลา (กัปตันบอกลูบนมเลย ไม่เอากลัวได้แฟนที่นี้ เอ้าไปที่ไหนก็กลัวหมด บวชพระป่ะ 555+)

แต่เพลงนี้มันเพราะจริงๆ นะถึงแม้จะเศร้านิดหน่อย ไปตรงนั่นได้ยังไง และจุดสุดท้ายนั่นคือเชียงใหม่ ซึ่งช่วงระหว่างกำลังจะขึ้นเครื่องไปเชียงใหม่ อ้าวเกิดแผ่นดินไหวชะงั้น ซึ่งเชียงใหม่นั้น มีร้านใน btcmap เยอะพอสมควรและมีแวะไปร้านหนึ่งกลายเป็นว่าไม่รับชะแล้ว จะมีกี่ร้านที่ผมไปแวะเยี่ยมชิม ติดตามใน ตอนสุดท้ายในบทความกับ ep4

ท้ายนี้ผมเปิดเพจบนเมนสตรีมละเน้อ ตามได้ในเพจ ไปกับจิ๊บ (บนเฟสบุ๊ค) ผมคงเอาไว้แอบติดตามเพื่อนบน nostr บนเฟสบุ๊คที่พอที่จะติดตามได้บ้าง น่าจะได้อ่านอะไรต่างๆที่ใหลมา คงเอาไว้เขียนรีวิวประสบการณ์การท่องเที่ยวส่วนตัว เพื่อนสมัยเรียนผมเคยบอกว่ามึงไปเที่ยวบ่อยมึงไม่เขียนลงบ้างวะ ไม่เอาขี้เกียจวะ ไม่รู้จะดึงพลังงานตอนทำเพจสมัยมอปลายได้หรือไม่ ก็ไม่รู้เหมือนกัน เอาไว้ส่องๆโปรไฟล์ใครบน nostr ที่อยู่บนเฟสแหละ ฮ่าๆ เป็นเพจอยากเล่าอะไรก็อยากเล่า และแว๊บไปคอมเมนต์เพื่อนๆ บน nostr บ้าง ขอบคุณครับ
-
 @ 7bc05901:8c26d22b
2025-04-09 14:15:31
@ 7bc05901:8c26d22b
2025-04-09 14:15:31My wife (girlfriend at the time) and I were heading back from Nashville after celebrating the opening of Bitcoin Park in Nashville. My boy Ryan had, once again, drug me to a Bitcoin event in the waning days of my stubborn shitcoinery. This event was the nail in the coffin for those days, and I'm happy to say the "stay humble stack sats" message finally permeated.
My wife is a dedicated reseller, her family has been flipping garage sale finds and auction grabs for years, so we rarely see a flea market or antique mall that we pass up. Somewhere between Missouri and Nashville we pulled off the highway to check out a spot in a dying but (if you squint your eyes and imagine it is 50 years in the past) a picturesque little town.
We were in my little Scion FRS, a two door sports car, so when I came across an old newspaper vending machine, I had to do a lot of geometry to figure out if I could shove this thing in the Scion. I concluded that my girlfriend would have to ride in the backseat for the remaining three hour drive if I really wanted to scoop up this vending machine, because it was too wide to slide into the trunk. Even though she knew I had an infatuation for retro newspaper things and was encouraging me to buy it, I declined. Probably the right call, but I still think about that thing -- the price was right.
I don't know what I would have done with it, but I have for years produced various hobbyist newspaper zines focusing on local political issues that I distributed from the coffeeshop that I worked at in my small town. The idea was hitting so hard when the social media censorship conversation was at a fever pitch after 2016 -- You can't censor a copy machine, I kept thinking. Analog zines, I was convinced, were the future.
I hadn't thought through decentralized social media protocols, but I did get really tired of distributing zines that nobody was excited to pay me for. Copying, organizing, stapling. I should have known I didn't have the patience to maintain that, or the finances.
Even established local news corporations, especially in my town, are struggling to justify a print version. This wasn't the case a quarter of a century ago.
My dad would stop at the Casey's convenience story every morning on the way into town, as he took us to school. If you brought your own travel mug, it was only fifty cents to fill up your cup of coffee. Nearly everyday, he would also come out with a copy of the local newspaper: The Daily Journal. The price was right around a dollar for the paper. It might have even been cheaper, like fifty or seventy-five cents.
The idea I am inching towards in this post, is that if every person valued the distribution of local (and global) news to the tune of a buck or a buck fifty, we could see the re-emergence sustaining news ecosystems. A buck fifty is almost two thousand sats today -- imagine if each appreciator of local news set aside just a thousand sats a day to zap news distributors. If there was a bias for following and amplifying local news events in each user's town, which tend to get a lot of attention on the centralized social media platforms, I think an entirely new value-4-value journalism enterprise model could emerge.
It may be important to start tinkering on a client that is built specifically for newspapers. I am not sure which features would be critical, but as the normies trickle over to the uncensorable social media protocol -- let's be ready.
-
 @ fbf0e434:e1be6a39
2025-04-09 14:09:08
@ fbf0e434:e1be6a39
2025-04-09 14:09:08Hackathon 概要
近日, Sonic DeFAI 黑客松圆满落幕,在 Sonic 区块链生态系统中掀起参与热潮与创新风暴。此次活动共吸引 822 名开发者注册,最终 47 个项目通过审核。在四周赛程里,参赛者们开发新型 AI 代理,角逐总计 29.5 万美元的奖池。这些代理旨在参与社交及链上活动,助力提升 DeFAI(人工智能驱动的去中心化金融)。
赛事核心创新聚焦自主代理整合,部分亮点项目运用 Zerebro 及其开源框架 ZerePy,展现了 Sonic 每秒 10000 笔交易(TPS)的高处理性能与次秒级最终性,同时凸显其与以太坊的无缝流动性集成优势。
本次黑客松评审标准注重技术实施、设计、潜在影响力及创意,提交项目由行业专家团队评估,其中包括 Sonic Labs 首席执行官 Michael Kong。活动充分突显 Sonic 通过创新 AI 应用与强大区块链基础设施,推动去中心化金融未来发展的实力。
Hackathon 获胜者
最佳代理综合奖获奖者
- Shogun: DeFAi super vault's - 一个由 AI 驱动的 DeFi 协议,通过动态资本分配和再平衡来优化去中心化金融金库的收益。
- Nuvolari.Ai - 利用 AI 代理提高链上财务决策的个人理财助手。
- Hyper Sonic - 一个支持表情包币创新的去中心化枢纽,整合了博彩市场、启动平台和 AI 驱动的功能。
- Paintswap Game Engine - 一个 Web3 dApp,通过 AI 驱动的提示实现游戏创作,民主化游戏开发过程。
- SUPERSONIC - 一个由 AI 驱动的平台,自动识别 Web3 生态系统中的套利机会。
最佳社交代理奖获奖者
- Memegents - 结合 AI 和区块链创建个性化 AI 代理和加密货币代币。
- deChat: AI-Powered DeFi Interface for Sonic - 一个 AI 聊天界面,通过自然语言命令简化 DeFi 交互。
- CurtAIs - 通过一个集成 Telegram 的知识库促进 Sonic Labs 的引导。
最佳 DeFAI 代理奖获奖者
- SonicChat - 一个整合钱包管理、交易分析和 AI 驱动见解的平台。
- NoRugz - 促进 meme 币的创建和推广,并与社交媒体集成。
- Shiami - DeFAI for Everyone on Sonic - 一个简化 Sonic 上 DeFi 操作的便捷聊天机器人。
最佳工具代理奖获奖者
- Sonic's Risk Watch - 提供 Sonic 生态系统中的风险评估和投资组合优化。
- Knowscroll - 将社交媒体转化为 AI 生成内容的微学习体验。
最佳 deBridge 集成奖获奖者
- Crème'ai - 一个由 AI 驱动的投资组合顾问,通过实时数据优化加密管理。
- deChat: AI-Powered DeFi Interface for Sonic
- DogBone - 一个简化 DeFi 交互的平台,利用自动化和自然语言处理。
最佳 Allora 集成奖获奖者
- Sonic TradeZo - 一个去中心化、匿名的 AI 驱动博彩游戏,配有 AI 交易代理。
- Shogun: DeFAi super vault's
- AIm — Artificial Intelligence Manager - 自动化创建 AI 驱动的 DeFi 代理以优化 Sonic 上的财务交互。
DWF Labs 赞助的赛道奖获奖者
- Shogun: DeFAi super vault's
- Crème'ai
- EdgerAI - 利用基于社交信号和智能合约的链上交易策略。
有关项目的完整列表,请访问 Sonic DeFAI Hackathon 页面。
关于组织者
Sonic Labs
Sonic Labs 专注于区块链解决方案,利用在去中心化技术方面的广泛专业知识。该组织开发了提升数据安全性和交易效率的项目,并因创建可扩展的区块链基础设施和实施智能合约而闻名。目前,Sonic Labs 通过主导各种计划来实现无缝区块链技术集成,专注于扩大其在各个领域的影响。
-
 @ fbf0e434:e1be6a39
2025-04-09 14:07:49
@ fbf0e434:e1be6a39
2025-04-09 14:07:49Hackathon 概要
EurekaHACKS 是加拿大奥克维尔市 Abbey Park 高中主办的年度 12 小时黑客马拉松,主要面向高中生群体。今年共有 92 名参与者,最终 51 个项目通过审核。作为哈顿地区规模最大的高中生黑客马拉松之一,活动开设技术研讨会,提供超 7000 美元奖金,营造出充满竞争的氛围。
赛事分设多个奖项:“最佳整体 Hack” 获奖者可获 Bambu Lab A1 Minis,亚军能得到 Red Dragon 机械键盘;其他奖项用于表彰在本地影响力、创造力及技术专长方面表现突出的项目。其中,运用 Internet Computer Protocol(ICP)的项目最高可获 500 美元奖励,涉及 Vectara 的项目可获 300 美元积分。技术研讨会环节还设有 Jane Street 卡片、泡泡茶及各类代金券等奖励。
这场黑客马拉松将年轻创新者汇聚一堂,激发创造力,促进技术技能提升,同时彰显了当地社区的高度参与。
Hackathon 获奖者
标准赛道奖项得主
2025 年 EurekaHacks 标准赛道的参赛者需让项目贴合特定主题,由此催生出多样的技术创新成果。
最佳整体Hack
- FaunaDex: 这款应用通过使用AI识别真实动物并提供详细信息来促进自然探索,鼓励户外活动和学习。
亚军Hack
- ArcaneStep: 将网页游戏与现实中的身体活动结合,ArcaneStep激励孩子们通过行走收集法力以施放法术,旨在减少屏幕时间。
终极编码者第三名
- LocalLink: LocalLink利用地理空间技术连接户外空间中的个人,以促进社区参与,提供即时、有意义的互动。
最佳本地影响
- Gems: Gems是一个基于地图的界面,促进城市探索,使用户能够发现和分享独特的地点,增强探索体验。
最具触感
- Greenlight: 这个游戏化应用鼓励户外活动,用户可通过体育锻炼和自然互动获得积分。
最佳展示
- The Moss Garden: The Moss Garden旨在提高用户的生产力,通过自然主题的网站来增强与自然的联系,提高专注力和心理健康。
终极编码者最佳年轻黑客
- socialize.ai: 利用AI代理,socialize.ai为在线互动提供对话提示和反向图像搜索功能,以增强社交互动。
如需获取完整项目列表,请访问 EurekaHacks 2025 Buidl Page。
关于主办方
EurekaHACKS
EurekaHACKS以促进技术创新着称,特别是在区块链和技术开发领域。通过组织各种hackathons,它连接了技术爱好者并支持协作项目开发。这些活动推动了去中心化应用程序的显著进展,为区块链社区做出了重要贡献。EurekaHACKS目前专注于培养新的人才,并通过教育项目和专项活动推广可持续技术解决方案。
-
 @ 88cc134b:5ae99079
2025-04-09 12:29:29
@ 88cc134b:5ae99079
2025-04-09 12:29:29 -
 @ 88cc134b:5ae99079
2025-04-09 11:34:56
@ 88cc134b:5ae99079
2025-04-09 11:34:56text
-
 @ 04c195f1:3329a1da
2025-04-09 10:54:43
@ 04c195f1:3329a1da
2025-04-09 10:54:43The old world order is crumbling. What was once considered stable and unshakable—the American-led global framework established after World War II—is now rapidly disintegrating. From the fraying fabric of NATO to the self-serving protectionism of Trump’s renewed presidency, the signals are clear: the empire that once held the Western world together is retreating. And in the vacuum it leaves behind, a new power must emerge.
The question is: will Europe finally seize this moment?
For decades, Europe has relied on the illusion of safety under an American umbrella. This dependency allowed us to indulge in what can only be described as “luxury politics.” Instead of strengthening our core institutions—defense, infrastructure, energy independence—we poured our energy into ideological experiments: value-based governance, multiculturalism, aggressive climate goals, and endless layers of bureaucracy.
We let ourselves believe history had ended. That war, scarcity, and geopolitical struggle were things of the past. That our greatest challenges would be inclusivity, carbon credits, and data protection regulations.
But history, as always, had other plans.
Trump, Nationalist Hope and Hard Reality
Across Europe, many nationalists and conservatives initially welcomed Donald Trump. He rejected the tenets of liberal globalism, called out the absurdities of woke ideology, and promised a return to realism. In a world saturated by progressive conformity, he seemed like a disruptive breath of fresh air.
And to a certain extent, he was.
But history will likely remember his presidency not for culture wars or conservative rhetoric—but for something far more consequential: the dismantling of the American empire.
What we are witnessing under Trump is the accelerated withdrawal of the United States from its role as global enforcer. Whether by design or incompetence, the result is the same. American institutions are retracting, its alliances are fraying, and its strategic grip on Europe is loosening.
For Americans, this may seem like decline. For Europe, it is an opportunity—an uncomfortable, painful, but necessary opportunity.
This is our chance to break free from the American yoke and step into the world as a sovereign power in our own right.
The End of Illusions
Europe is not a weak continent. We have a population larger than the United States, an economy that outpaces Russia’s many times over, and centuries of civilizational strength behind us. But we have been kept fragmented, distracted, and dependent—by design.
Both Washington and Moscow have an interest in a divided, impotent Europe. American strategists see us as junior partners at best, liabilities at worst. Russian elites, like Sergey Karaganov, openly admit their goal is to push Europe off the global stage. China, for its part, eyes our markets while quietly maneuvering to undermine our autonomy.
But something is changing.
In Brussels, even the ideologically captured technocrats are beginning to see the writing on the wall. Overbearing regulations like GDPR are being reconsidered. The long-pushed Equal Treatment Directive—a pan-European anti-discrimination law—may finally be scrapped. These are small signs, but signs nonetheless. Europe is waking up.
From Fracture to Foundation
To build something new, the old must first fall. That collapse is now well underway.
The collapse of American hegemony does not mean the rise of chaos—it means the opening of a path. Europe has a choice: continue to drift, clinging to broken institutions and obsolete alliances, or embrace the challenge of becoming a serious actor in a multipolar world.
This does not mean copying the imperial ambitions of others. Europe’s strength will not come from domination, but from independence, coherence, and confidence. A strong Europe is not one ruled from Brussels, but one composed of strong, rooted nations acting together in strategic alignment. Not a federation, not an empire in the classical sense—but a civilization asserting its right to survive and thrive on its own terms.
At the same time, we must not fall into the trap of romantic isolationism. Some nationalists still cling to the idea that their nation alone can stand firm on the global stage, detached from continental collaboration. That vision no longer matches the geopolitical reality. The world has changed, and so must our strategy. In key areas—such as defense, border security, trade policy, and technological sovereignty—Europe must act with unity and purpose. This does not require dissolving national identities; it requires mature cooperation among free nations. To retreat into purely national silos would be to condemn Europe to irrelevance. Strengthening the right kind of European cooperation—while returning power in other areas to the national level—is not a betrayal of nationalism, but its necessary evolution.
A Third Position: Beyond East and West
As the American empire stumbles and Russia attempts to fill the void, Europe must not become a pawn in someone else’s game. Our task is not to shift allegiance from one master to another—but to step into sovereignty. This is not about trading Washington for Moscow, or Beijing. It is about rejecting all external domination and asserting our own geopolitical will.
A truly pro-European nationalism must recognize that our civilizational future lies not in nostalgia or subservience, but in strategic clarity. We must build a third position—a pole of stability and power that stands apart from the decaying empires of the past.
That requires sacrifice, but it also promises freedom.
Hope Through Action
There is a romantic notion among some European nationalists that decline is inevitable—that we are simply passengers on a sinking ship. But fatalism is not tradition. It is surrender.
Our ancestors did not build cathedrals, repel invaders, or chart the globe by giving in to despair. They acted—often against impossible odds—because they believed in a Europe worth fighting for.
We must now rediscover that spirit.
This is not a call for uniformity, but for unity. Not for empire, but for sovereignty. Not for nostalgia, but for renewal. Across the continent, a new consciousness is stirring. From the Alps to the Baltic, from Lisbon to Helsinki, there are voices calling for something more than submission to global markets and American whims.
They are calling for Europe.
The Hour Has Come
There may not be a second chance. The tide of history is turning, and the next ten years will determine whether Europe reclaims its role in the world—or becomes a museum piece, mourned by tourists and remembered by none.
This is not the end.
It is our beginning—if we are brave enough to seize it.
■
-
 @ 7d33ba57:1b82db35
2025-04-09 08:25:02
@ 7d33ba57:1b82db35
2025-04-09 08:25:02Sagres, perched on the dramatic cliffs of Portugal’s Algarve, feels like the end of the world—and in the best way. It's a small, laid-back town with a surfer vibe, windswept beaches, and rugged coastal views that are simply breathtaking. If you’re into nature, chill vibes, and jaw-dropping sunsets, Sagres is your spot.
🌟 Top Things to See & Do in Sagres
1️⃣ Cabo de São Vicente (Cape St. Vincent)
- The southwesternmost point of mainland Europe
- Home to a dramatic cliffside lighthouse and epic sunsets
- Once thought to be the "end of the world" in ancient times
2️⃣ Fortaleza de Sagres
- A 15th-century fortress with a giant stone compass, sea views, and a coastal walking path
- Linked to Henry the Navigator and Portugal’s Age of Discoveries
- Simple, scenic, and full of history
3️⃣ Surf the Waves 🌊
- Some of the best surfing beaches in Europe
- Try Praia do Tonel or Praia do Beliche—great for both beginners and pros
- Tons of surf schools and rental shops around town
4️⃣ Chill on the Beaches
- Praia da Mareta – calm and central, perfect for swimming
- Praia do Beliche – surrounded by cliffs, more secluded
- Praia do Martinhal – family-friendly with shallow water
5️⃣ Coastal Hiking & Cliffs
- Walk along the Rota Vicentina trails for raw Atlantic views, wildflowers, and sea breeze
- Bring water and a camera—it's a nature-lover’s dream
🍽️ What to Eat in Sagres
- Fresh seafood – grilled sardines, octopus salad, and cataplana
- Percebes (goose barnacles) – a local delicacy from the rocks
- Pastéis de nata – always a good idea ☕
- Pair it all with a cold Super Bock or a glass of vinho verde
Try beachside spots or cozy taverns in town—nothing too fancy, just simple, tasty, and fresh.
🏄 Vibe & Tips
✅ Sagres is quiet, remote, and windswept—perfect if you're looking to unwind
✅ Great for vanlifers, surfers, hikers, and sunset chasers
✅ Bring layers—it can be windy, even in summer
✅ Sunsets at Cabo de São Vicente are legendary—get there early for a good spot
✅ A car helps to explore the nearby coastlines and hidden beaches -
 @ 39cc53c9:27168656
2025-04-09 07:59:35
@ 39cc53c9:27168656
2025-04-09 07:59:35The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ 39cc53c9:27168656
2025-04-09 07:59:33
@ 39cc53c9:27168656
2025-04-09 07:59:33Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 39cc53c9:27168656
2025-04-09 07:59:32
@ 39cc53c9:27168656
2025-04-09 07:59:32Over the past few months, I've dedicated my time to a complete rewrite of the kycnot.me website. The technology stack remains unchanged; Golang paired with TailwindCSS. However, I've made some design choices in this iteration that I believe significantly enhance the site. Particularly to backend code.
UI Improvements
You'll notice a refreshed UI that retains the original concept but has some notable enhancements. The service list view is now more visually engaging, it displays additional information in a more aesthetically pleasing manner. Both filtering and searching functionalities have been optimized for speed and user experience.
Service pages have been also redesigned to highlight key information at the top, with the KYC Level box always accessible. The display of service attributes is now more visually intuitive.
The request form, especially the Captcha, has undergone substantial improvements. The new self-made Captcha is robust, addressing the reliability issues encountered with the previous version.
Terms of Service Summarizer
A significant upgrade is the Terms of Service summarizer/reviewer, now powered by AI (GPT-4-turbo). It efficiently condenses each service's ToS, extracting and presenting critical points, including any warnings. Summaries are updated monthly, processing over 40 ToS pages via the OpenAI API using a self-crafted and thoroughly tested prompt.
Nostr Comments
I've integrated a comment section for each service using Nostr. For guidance on using this feature, visit the dedicated how-to page.
Database
The backend database has transitioned to pocketbase, an open-source Golang backend that has been a pleasure to work with. I maintain an updated fork of the Golang SDK for pocketbase at pluja/pocketbase.
Scoring
The scoring algorithm has also been refined to be more fair. Despite I had considered its removal due to the complexity it adds (it is very difficult to design a fair scoring system), some users highlighted its value, so I kept it. The updated algorithm is available open source.
Listings
Each listing has been re-evaluated, and the ones that were no longer operational were removed. New additions are included, and the backlog of pending services will be addressed progressively, since I still have access to the old database.
API
The API now offers more comprehensive data. For more details, check here.
About Page
The About page has been restructured for brevity and clarity.
Other Changes
Extensive changes have been implemented in the server-side logic, since the whole code base was re-written from the ground up. I may discuss these in a future post, but for now, I consider the current version to be just a bit beyond beta, and additional updates are planned in the coming weeks.
-
 @ 39cc53c9:27168656
2025-04-09 07:59:30
@ 39cc53c9:27168656
2025-04-09 07:59:30I'm launching a new service review section on this blog in collaboration with OrangeFren. These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Reviews are done in advance, then, the service provider has the discretion to approve publication without modifications.
Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing.
The review
WizardSwap is an instant exchange centred around privacy coins. It was launched in 2020 making it old enough to have weathered the 2021 bull run and the subsequent bearish year.
| Pros | Cons | |------|------| | Tor-friendly | Limited liquidity | | Guarantee of no KYC | Overly simplistic design | | Earn by providing liquidity | |
Rating: ★★★★★ Service Website: wizardswap.io
Liquidity
Right off the bat, we'll start off by pointing out that WizardSwap relies on its own liquidity reserves, meaning they aren't just a reseller of Binance or another exchange. They're also committed to a no-KYC policy, when asking them, they even promised they would rather refund a user their original coins, than force them to undergo any sort of verification.
On the one hand, full control over all their infrastructure gives users the most privacy and conviction about the KYC policies remaining in place.
On the other hand, this means the liquidity available for swapping isn't huge. At the time of testing we could only purchase at most about 0.73 BTC with XMR.
It's clear the team behind WizardSwap is aware of this shortfall and so they've come up with a solution unique among instant exchanges. They let you, the user, deposit any of the currencies they support into your account and earn a profit on the trades made using your liquidity.
Trading
Fees on WizardSwap are middle-of-the-pack. The normal fee is 2.2%. That's more than some exchanges that reserve the right to suddenly demand you undergo verification, yet less than half the fees on some other privacy-first exchanges. However as we mentioned in the section above you can earn almost all of that fee (2%) if you provide liquidity to WizardSwap.
It's good that with the current Bitcoin fee market their fees are constant regardless of how much, or how little, you send. This is in stark contrast with some of the alternative swap providers that will charge you a massive premium when attempting to swap small amounts of BTC away.
Test trades
Test trades are always performed without previous notice to the service provider.
During our testing we performed a few test trades and found that every single time WizardSwap immediately detected the incoming transaction and the amount we received was exactly what was quoted before depositing. The fees were inline with what WizardSwap advertises.

- Monero payment proof
- Bitcoin received
- Wizardswap TX link - it's possible that this link may cease to be valid at some point in the future.
ToS and KYC
WizardSwap does not have a Terms of Service or a Privacy Policy page, at least none that can be found by users. Instead, they offer a FAQ section where they addresses some basic questions.
The site does not mention any KYC or AML practices. It also does not specify how refunds are handled in case of failure. However, based on the FAQ section "What if I send funds after the offer expires?" it can be inferred that contacting support is necessary and network fees will be deducted from any refund.
UI & Tor
WizardSwap can be visited both via your usual browser and Tor Browser. Should you decide on the latter you'll find that the website works even with the most strict settings available in the Tor Browser (meaning no JavaScript).
However, when disabling Javascript you'll miss the live support chat, as well as automatic refreshing of the trade page. The lack of the first means that you will have no way to contact support from the trade page if anything goes wrong during your swap, although you can do so by mail.
One important thing to have in mind is that if you were to accidentally close the browser during the swap, and you did not save the swap ID or your browser history is disabled, you'll have no easy way to return to the trade. For this reason we suggest when you begin a trade to copy the url or ID to someplace safe, before sending any coins to WizardSwap.
The UI you'll be greeted by is simple, minimalist, and easy to navigate. It works well not just across browsers, but also across devices. You won't have any issues using this exchange on your phone.
Getting in touch
The team behind WizardSwap appears to be most active on X (formerly Twitter): https://twitter.com/WizardSwap_io
If you have any comments or suggestions about the exchange make sure to reach out to them. In the past they've been very receptive to user feedback, for instance a few months back WizardSwap was planning on removing DeepOnion, but the community behind that project got together ^1 and after reaching out WizardSwap reversed their decision ^2.
You can also contact them via email at:
support @ wizardswap . ioDisclaimer
None of the above should be understood as investment or financial advice. The views are our own only and constitute a faithful representation of our experience in using and investigating this exchange. This review is not a guarantee of any kind on the services rendered by the exchange. Do your own research before using any service.
-
 @ 39cc53c9:27168656
2025-04-09 07:59:28
@ 39cc53c9:27168656
2025-04-09 07:59:28Bitcoin enthusiasts frequently and correctly remark how much value it adds to Bitcoin not to have a face, a leader, or a central authority behind it. This particularity means there isn't a single person to exert control over, or a single human point of failure who could become corrupt or harmful to the project.
Because of this, it is said that no other coin can be equally valuable as Bitcoin in terms of decentralization and trustworthiness. Bitcoin is unique not just for being first, but also because of how the events behind its inception developed. This implies that, from Bitcoin onwards, any coin created would have been created by someone, consequently having an authority behind it. For this and some other reasons, some people refer to Bitcoin as "The Immaculate Conception".
While other coins may have their own unique features and advantages, they may not be able to replicate Bitcoin's community-driven nature. However, one other cryptocurrency shares a similar story of mystery behind its creation: Monero.
History of Monero
Bytecoin and CryptoNote
In March 2014, a Bitcointalk thread titled "Bytecoin. Secure, private, untraceable since 2012" was initiated by a user under the nickname "DStrange"^1^. DStrange presented Bytecoin (BCN) as a unique cryptocurrency, in operation since July 2012. Unlike Bitcoin, it employed a new algorithm known as CryptoNote.
DStrange apparently stumbled upon the Bytecoin website by chance while mining a dying bitcoin fork, and decided to create a thread on Bitcointalk^1^. This sparked curiosity among some users, who wondered how could Bytecoin remain unnoticed since its alleged launch in 2012 until then^2^.
Some time after, a user brought up the "CryptoNote v2.0" whitepaper for the first time, underlining its innovative features^4^. Authored by the pseudonymous Nicolas van Saberhagen in October 2013, the CryptoNote v2 whitepaper^5^ highlighted the traceability and privacy problems in Bitcoin. Saberhagen argued that these flaws could not be quickly fixed, suggesting it would be more efficient to start a new project rather than trying to patch the original^5^, an statement simmilar to the one from Satoshi Nakamoto^6^.
Checking with Saberhagen's digital signature, the release date of the whitepaper seemed correct, which would mean that Cryptonote (v1) was created in 2012^7^, although there's an important detail: "Signing time is from the clock on the signer's computer" ^9^.
Moreover, the whitepaper v1 contains a footnote link to a Bitcointalk post dated May 5, 2013^10^, making it impossible for the whitepaper to have been signed and released on December 12, 2012.
As the narrative developed, users discovered that a significant 80% portion of Bytecoin had been pre-mined^11^ and blockchain dates seemed to be faked to make it look like it had been operating since 2012, leading to controversy surrounding the project.
The origins of CryptoNote and Bytecoin remain mysterious, leaving suspicions of a possible scam attempt, although the whitepaper had a good amount of work and thought on it.
The fork
In April 2014, the Bitcointalk user
thankful_for_today, who had also participated in the Bytecoin thread^12^, announced plans to launch a Bytecoin fork named Bitmonero^13^.The primary motivation behind this fork was "Because there is a number of technical and marketing issues I wanted to do differently. And also because I like ideas and technology and I want it to succeed"^14^. This time Bitmonero did things different from Bytecoin: there was no premine or instamine, and no portion of the block reward went to development.
However, thankful_for_today proposed controversial changes that the community disagreed with. Johnny Mnemonic relates the events surrounding Bitmonero and thankful_for_today in a Bitcointalk comment^15^:
When thankful_for_today launched BitMonero [...] he ignored everything that was discussed and just did what he wanted. The block reward was considerably steeper than what everyone was expecting. He also moved forward with 1-minute block times despite everyone's concerns about the increase of orphan blocks. He also didn't address the tail emission concern that should've (in my opinion) been in the code at launch time. Basically, he messed everything up. Then, he disappeared.
After disappearing for a while, thankful_for_today returned to find that the community had taken over the project. Johnny Mnemonic continues:
I, and others, started working on new forks that were closer to what everyone else was hoping for. [...] it was decided that the BitMonero project should just be taken over. There were like 9 or 10 interested parties at the time if my memory is correct. We voted on IRC to drop the "bit" from BitMonero and move forward with the project. Thankful_for_today suddenly resurfaced, and wasn't happy to learn the community had assumed control of the coin. He attempted to maintain his own fork (still calling it "BitMonero") for a while, but that quickly fell into obscurity.
The unfolding of these events show us the roots of Monero. Much like Satoshi Nakamoto, the creators behind CryptoNote/Bytecoin and thankful_for_today remain a mystery^17^, having disappeared without a trace. This enigma only adds to Monero's value.
Since community took over development, believing in the project's potential and its ability to be guided in a better direction, Monero was given one of Bitcoin's most important qualities: a leaderless nature. With no single face or entity directing its path, Monero is safe from potential corruption or harm from a "central authority".
The community continued developing Monero until today. Since then, Monero has undergone a lot of technological improvements, migrations and achievements such as RingCT and RandomX. It also has developed its own Community Crowdfundinc System, conferences such as MoneroKon and Monerotopia are taking place every year, and has a very active community around it.
Monero continues to develop with goals of privacy and security first, ease of use and efficiency second. ^16^
This stands as a testament to the power of a dedicated community operating without a central figure of authority. This decentralized approach aligns with the original ethos of cryptocurrency, making Monero a prime example of community-driven innovation. For this, I thank all the people involved in Monero, that lead it to where it is today.
If you find any information that seems incorrect, unclear or any missing important events, please contact me and I will make the necessary changes.
Sources of interest
- https://forum.getmonero.org/20/general-discussion/211/history-of-monero
- https://monero.stackexchange.com/questions/852/what-is-the-origin-of-monero-and-its-relationship-to-bytecoin
- https://en.wikipedia.org/wiki/Monero
- https://bitcointalk.org/index.php?topic=583449.0
- https://bitcointalk.org/index.php?topic=563821.0
- https://bitcointalk.org/index.php?action=profile;u=233561
- https://bitcointalk.org/index.php?topic=512747.0
- https://bitcointalk.org/index.php?topic=740112.0
- https://monero.stackexchange.com/a/1024
- https://inspec2t-project.eu/cryptocurrency-with-a-focus-on-anonymity-these-facts-are-known-about-monero/
- https://medium.com/coin-story/coin-perspective-13-riccardo-spagni-69ef82907bd1
- https://www.getmonero.org/resources/about/
- https://www.wired.com/2017/01/monero-drug-dealers-cryptocurrency-choice-fire/
- https://www.monero.how/why-monero-vs-bitcoin
- https://old.reddit.com/r/Monero/comments/u8e5yr/satoshi_nakamoto_talked_about_privacy_features/
-
 @ 39cc53c9:27168656
2025-04-09 07:59:27
@ 39cc53c9:27168656
2025-04-09 07:59:27I've been thinking about how to improve my seed backup in a cheap and cool way, mostly for fun. Until now, I had the seed written on a piece of paper in a desk drawer, and I wanted something more durable and fire-proof.
After searching online, I found two options I liked the most: the Cryptosteel Capsule and the Trezor Keep. These products are nice but quite expensive, and I didn't want to spend that much on my seed backup. Privacy is also important, and sharing details like a shipping address makes me uncomfortable. This concern has grown since the Ledger incident^1. A $5 wrench attack^2 seems too cheap, even if you only hold a few sats.
Upon seeing the design of Cryptosteel, I considered creating something similar at home. Although it may not be as cool as their device, it could offer almost the same in terms of robustness and durability.
Step 1: Get the materials and tools
When choosing the materials, you will want to go with stainless steel. It is durable, resistant to fire, water, and corrosion, very robust, and does not rust. Also, its price point is just right; it's not the cheapest, but it's cheap for the value you get.

I went to a material store and bought:
- Two bolts
- Two hex nuts and head nuts for the bolts
- A bag of 30 washers
All items were made of stainless steel. The total price was around €6. This is enough for making two seed backups.
You will also need:
- A set of metal letter stamps (I bought a 2mm-size letter kit since my washers were small, 6mm in diameter)
- You can find these in local stores or online marketplaces. The set I bought cost me €13.
- A good hammer
- A solid surface to stamp on
Total spent: 19€ for two backups
Step 2: Stamp and store
Once you have all the materials, you can start stamping your words. There are many videos on the internet that use fancy 3D-printed tools to get the letters nicely aligned, but I went with the free-hand option. The results were pretty decent.

I only stamped the first 4 letters for each word since the BIP-39 wordlist allows for this. Because my stamping kit did not include numbers, I used alphabet letters to define the order. This way, if all the washers were to fall off, I could still reassemble the seed correctly.
The final result
So this is the final result. I added two smaller washers as protection and also put the top washer reversed so the letters are not visible:

Compared to the Cryptosteel or the Trezor Keep, its size is much more compact. This makes for an easier-to-hide backup, in case you ever need to hide it inside your human body.
Some ideas
Tamper-evident seal
To enhance the security this backup, you can consider using a tamper-evident seal. This can be easily achieved by printing a unique image or using a specific day's newspaper page (just note somewhere what day it was).
Apply a thin layer of glue to the washer's surface and place the seal over it. If someone attempts to access the seed, they will be forced to destroy the seal, which will serve as an evident sign of tampering.
This simple measure will provide an additional layer of protection and allow you to quickly identify any unauthorized access attempts.
Note that this method is not resistant to outright theft. The tamper-evident seal won't stop a determined thief but it will prevent them from accessing your seed without leaving any trace.
Redundancy
Make sure to add redundancy. Make several copies of this cheap backup, and store them in separate locations.
Unique wordset
Another layer of security could be to implement your own custom mnemonic dictionary. However, this approach has the risk of permanently losing access to your funds if not implemented correctly.
If done properly, you could potentially end up with a highly secure backup, as no one else would be able to derive the seed phrase from it. To create your custom dictionary, assign a unique number from 1 to 2048 to a word of your choice. Maybe you could use a book, and index the first 2048 unique words that appear. Make sure to store this book and even get a couple copies of it (digitally and phisically).
This self-curated set of words will serve as your personal BIP-39 dictionary. When you need to translate between your custom dictionary and the official BIP-39 wordlist, simply use the index number to find the corresponding word in either list.
Never write the idex or words on your computer (Do not use
Ctr+F) -
 @ 39cc53c9:27168656
2025-04-09 07:59:25
@ 39cc53c9:27168656
2025-04-09 07:59:25kycnot.me features a somewhat hidden tool that some users may not be aware of. Every month, an automated job crawls every listed service's Terms of Service (ToS) and FAQ pages and conducts an AI-driven analysis, generating a comprehensive overview that highlights key points related to KYC and user privacy.
Here's an example: Changenow's Tos Review

Why?
ToS pages typically contain a lot of complicated text. Since the first versions of kycnot.me, I have tried to provide users a comprehensive overview of what can be found in such documents. This automated method keeps the information up-to-date every month, which was one of the main challenges with manual updates.
A significant part of the time I invest in investigating a service for kycnot.me involves reading the ToS and looking for any clauses that might indicate aggressive KYC practices or privacy concerns. For the past four years, I performed this task manually. However, with advancements in language models, this process can now be somewhat automated. I still manually review the ToS for a quick check and regularly verify the AI’s findings. However, over the past three months, this automated method has proven to be quite reliable.
Having a quick ToS overview section allows users to avoid reading the entire ToS page. Instead, you can quickly read the important points that are grouped, summarized, and referenced, making it easier and faster to understand the key information.
Limitations
This method has a key limitation: JS-generated pages. For this reason, I was using Playwright in my crawler implementation. I plan to make a release addressing this issue in the future. There are also sites that don't have ToS/FAQ pages, but these sites already include a warning in that section.
Another issue is false positives. Although not very common, sometimes the AI might incorrectly interpret something harmless as harmful. Such errors become apparent upon reading; it's clear when something marked as bad should not be categorized as such. I manually review these cases regularly, checking for anything that seems off and then removing any inaccuracies.
Overall, the automation provides great results.
How?
There have been several iterations of this tool. Initially, I started with GPT-3.5, but the results were not good in any way. It made up many things, and important thigs were lost on large ToS pages. I then switched to GPT-4 Turbo, but it was expensive. Eventually, I settled on Claude 3 Sonnet, which provides a quality compromise between GPT-3.5 and GPT-4 Turbo at a more reasonable price, while allowing a generous 200K token context window.
I designed a prompt, which is open source^1, that has been tweaked many times and will surely be adjusted further in the future.
For the ToS scraping part, I initially wrote a scraper API using Playwright^2, but I replaced it with Jina AI Reader^3, which works quite well and is designed for this task.
Non-conflictive ToS
All services have a dropdown in the ToS section called "Non-conflictive ToS Reviews." These are the reviews that the AI flagged as not needing a user warning. I still provide these because I think they may be interesting to read.
Feedback and contributing
You can give me feedback on this tool, or share any inaccuraties by either opening an issue on Codeberg^4 or by contacting me ^5.
You can contribute with pull requests, which are always welcome, or you can support this project with any of the listed ways.
-
 @ 39cc53c9:27168656
2025-04-09 07:59:24
@ 39cc53c9:27168656
2025-04-09 07:59:24These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing. Reviews are in collaboration with Orangefren.
The review
Swapter.io is an all-purpose instant exchange. They entered the scene in the depths of the bear market about 2 years ago in June of 2022.
| Pros | Cons | | --------------- | ---------------------------------- | | Low fees | Shotgun KYC with opaque triggers | | Large liquidity | Relies on 3rd party liquidity | | Works over Tor | Front-end not synced with back-end | | Pretty UI | |
Rating: ★★★☆☆ Service Website: swapter.io
⚠️ There is an ongoing issue with this service: read more on Reddit.
Test Trades
During our testing we performed a trade from XMR to LTC, and then back to XMR.
Our first trade had the ID of:
mpUitpGemhN8jjNAjQuo6EvQ. We were promised 0.8 LTC for sending 0.5 XMR, before we sent the Monero. When the Monero arrived we were sent 0.799 LTC.On the return journey we performed trade with ID:
yaCRb5pYcRKAZcBqg0AzEGYg. This time we were promised 0.4815 XMR for sending 0.799 LTC. After Litecoin arrived we were sent 0.4765 XMR.As such we saw a discrepancy of
~0.1%in the first trade and~1%in the second trade. Considering those trades were floating we determine the estimates presented in the UI to be highly accurate and honest.Of course Swapter could've been imposing a large fee on their estimates, but we checked their estimates against CoinGecko and found the difference to be equivalent to a fee of just over
0.5%. Perfectly in line with other swapping services.Trading
Swapter supports BTC, LTC, XMR and well over a thousand other coins. Sadly they don't support the Lightning Network. For the myriad of currencies they deal with they provide massive upper limits. You could exchange tens, or even hundreds, of thousands of dollars worth of cryptocurrency in a single trade (although we wouldn't recommend it).
The flip side to this is that Swapter relies on 3rd party liquidity. Aside from the large liqudity this also benefits the user insofar as it allows for very low fees. However, it also comes with a negative - the 3rd party gets to see all your trades. Unfortunately Swapter opted not to share where they source their liquidity in their Privacy Policy or Terms of Service.
KYC & AML policies
Swapter reserves the right to require its users to provide their full name, their date of birth, their address and government-issued ID. A practice known as "shotgun KYC". This should not happen often - in our testing it never did - however it's not clear when exactly it could happen. The AML & KYC policy provided on Swapter's website simply states they will put your trade on hold if their "risk scoring system [deems it] as suspicious".
Worse yet, if they determine that "any of the information [the] customer provided is incorrect, false, outdated, or incomplete" then Swapter may decide to terminate all of the services they provide to the user. What exactly would happen to their funds in such a case remains unclear.
The only clarity we get is that the Swapter policy outlines a designated 3rd party that will verify the information provided by the user. The third party's name is Sum & Substance Ltd, also simply known as samsub and available at sumsub.com
It's understandable that some exchanges will decide on a policy of this sort, especially when they rely on external liquidity, but we would prefer more clarity be given. When exactly is a trade suspicious?
Tor
We were pleased to discover Swapter works over Tor. However, they do not provide a Tor mirror, nor do they work without JavaScript. Additionally, we found that some small features, such as the live chat, did not work over Tor. Fortunately, other means of contacting their support are still available.
UI
We have found the Swapter UI to be very modern, straightforward and simple to use. It's available in 4 languages (English, French, Dutch and Russian), although we're unable to vouch for the quality of some of those, the ones that we used seemed perfectly serviceable.
Our only issue with the UI was that it claims the funds have been sent following the trade, when in reality it seems to take the backend a minute or so to actually broadcast the transaction.
Getting in touch
Swapter's team has a chat on their website, a support email address and a support Telegram. Their social media presence in most active on Telegram and X (formerly Twitter).
Disclaimer
None of the above should be understood as investment or financial advice. The views are our own only and constitute a faithful representation of our experience in using and investigating this exchange. This review is not a guarantee of any kind on the services rendered by the exchange. Do your own research before using any service.
-
 @ 39cc53c9:27168656
2025-04-09 07:59:22
@ 39cc53c9:27168656
2025-04-09 07:59:22“The future is there... staring back at us. Trying to make sense of the fiction we will have become.” — William Gibson.
This month is the 4th anniversary of kycnot.me. Thank you for being here.
Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency free from government and institutional control. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play.
What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you.
Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances.
Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition^1:

How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us.
‟Hush now, baby, baby, don't you cry Mamma's gonna make all of your nightmares come true Mamma's gonna put all of her fears into you Mamma's gonna keep you right here, under her wing She won't let you fly, but she might let you sing Mamma's gonna keep baby cosy and warm” — Mother, Pink Floyd
We must resist any attack on our privacy and freedom. To do this, we must collaborate.
If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that.
If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can.
This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest.
“We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” — Eric Hughes, A Cypherpunk's Manifesto
The anniversary
Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of kycnot.me — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now.
kycnot.me has remained 100% independent and 100% open source^2 all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years).
The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see the score summary for any service's score.
I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this.
-
 @ 39cc53c9:27168656
2025-04-09 07:59:20
@ 39cc53c9:27168656
2025-04-09 07:59:20
Silent.link is an anonymous eSIM provider. They offer pay-as-you-go roaming in 160+ countries.
Pros
- Anonymous
- Private payment options
- High performance
- Global availability
Cons
- Need to select the right networks sometimes
- Latency
- Data and incoming SMS & call only
Rating
★★★★★
Service website
eSIMs replace traditional, physical SIM cards, if you have a fairly new phone, odds are it supports them. Since most people change their mobile carrier very rarely, the most common use case for these new eSIMs is their use in travel. Although their use as a piece of a larger OPSEC puzzle to improve privacy when using the internet from your phone is increasingly popular too.
Silent.link is not the only eSIM provider out there. Yet, they’re so unique that even Twitter’s (now X) founder Jack Dorsey recommends them.
Let’s start off with a quick explanation of how Silent.link works and what pay-as-you-go means. Most other eSIM providers will sell you packages of GBs with an expiration date. For instance imagine you’re visiting France then going to the UK after a few months. With other providers you might buy a 10GB in France package valid for 7 days, then after some months a 10GB in the UK package also valid for 7 days. You likely won’t use up the full package in either country and the remaining capacity will be voided as the package expires.
Silent.link’s pay-as-you-go is different. There are no geographic packages. There are no expiration dates. You simply have a balance denominated in USD and are charged as you use up the data according to the pricing of whichever local carrier you’re connecting via.
Preparing for the same trips from the example above you’d simply top-up your Silent.link balance with $10. Then you’d use Silent.link in France paying $1.33/GB, you’d only be charged for the exact amount used, then you’d go to the UK and pay $1.54/GB from the balance you had left over from France. It doesn’t matter how much time passes between the trips, because Silent.link balances don’t expire. If you have a balance left over you can use it on a future trip, or simply use it up in your home country.
Pros
Anonymity
Silent.link is anonymous. Most other eSIM providers require some form of identification. This can be a traditional, full KYC, procedure involving your ID or passport numbers or, as seemingly innocent, as verifying your phone number with your main carrier. Regardless, a link between the eSIM you bought online and your identity is established.
In some countries you’ll be able to pick up a traditional SIM (or the new eSIM) from a local carrier without undergoing this verification. This can still be a hassle though. You’ll need to look up the laws before travelling, you’ll need to find a local store selling them, you’ll need to decide how you’ll pay privately, etc. And that’s the best case, that’s assuming the country you want to get the SIM in allows you to buy one anonymously.
Private payment methods
Silent.link only accepts cryptocurrency and according to their stats, most payments are made with Bitcoin (either onchain or using the Lightning Network) or with Monero. As such paying anonymously is not a problem. The use a self-hosted instance of BTCPay Server to process payments and operate their own LN node. The entire checkout process can be completed over Tor.
Cons
Network selection
Although you can skip the hassle of buying a new eSIM every time you travel it’s a good idea to look up the pricing of different mobile networks in the country you’re going to. The differences can be trivial, but can also be 100x. If a specific mobile network offers a much better deal, you’ll probably want to dive into your phone’s settings to make sure it only connects to that network.
High prices for some regions
Second issue can be that, especially for poorer countries, Silent.link might not have the best prices. For instance if you travel to Angola you’ll end up paying $155.44/GB. But if you search around for other providers you’ll find eSIM that offer much lower prices for that same country.
Data & incoming SMS & calls only
These eSIMs are either data-only or only offer data and inbound sms and calls. You can’t use Silent.link eSIMs to send texts or make phone calls.
Latency
For most use-cases this shouldn’t matter, but the way roaming works is that when you’re abroad your data is first sent to your home country then sent out into the internet from there. For instance if you’re a Brit on holiday in Spain wherever you open up a website your phone communicates with the Spanish network who forwards the request to your home network in the UK and only there does the request start going towards the website you’re trying to load. The response takes the same path in reverse.
The home network for the Silent.link eSIMs is Poland. To take an extreme (antipodal) example, if you’re in Chile loading a Chilean website your request will go to Poland then back from Poland to the website’s server in Chile, then the response will go from Chile to Poland to you (in Chile). All those trips add latency. In our testing, done during the recent OrangeFren.com meetup in Istanbul, the difference was an additional 73ms. The bandwidth, however, was exceptional, easily surpassing 100 Mbps.
This latency issue isn’t unique to Silent.link, other eSIM providers usually suffer from it too, though their home network may be better suited for your latency needs. If you need the best latency we recommend a SIM from a local provider (or WiFi).
This proxy behaviour isn’t all negative however. It may potentially allow you to circumvent censorship or geoblocking if you’re trying to access resources available from Poland, but unavailable elsewhere.
Besides Istanbul one of the countries we also tested Silent.link in was Northern Cyprus. This territory is mostly unrecognized. It’s a country that, depending on who you ask, is or isn’t real. Despite this unresolved geopolitical status Silent.link performed without any issues.
Installation
If you decide to give Silent.link a try, you'll need to select if you want a data-only plan or a plan with inbound SMS & calling, once you complete the payment simply scan the QR code on the order confirmation page with your phone. Make sure to save the url of that order confirmation page somewhere! You will need it to top up your eSIM and check your remaining balance.
Getting in touch
The preferred way of contacting Silent.link's support is using the website's built-in chat function. Alternative methods include X (formerly Twitter), Matrix and email.
Their support is online from 09:00 - 21:00 UTC although even when testing outside of those hours we got a reply within a minute.
NOTE: These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing.
-
 @ a367f9eb:0633efea
2025-04-09 07:28:49
@ a367f9eb:0633efea
2025-04-09 07:28:49WIEN – Diese Woche enthüllte Innenminister Gerhard Karner von der ÖVP, dass er einen Gesetzesentwurf "schnell" durchsetzen möchte, der der Regierung die Befugnis geben würde, verschlüsselte Kommunikation in Nachrichten-Apps zu überwachen.
Obwohl Karner betont hat, dass die neuen Befugnisse nur sehr gezielt eingesetzt würden, ist unklar, ob die Entwickler und Anbieter von Nachrichten-Apps gezwungen werden sollen, die Verschlüsselung zu brechen, um die Anordnungen durchzuführen.
Wie der stellvertretende Direktor des Consumer Choice Center, Yaël Ossowski, erklärte, würde diese Befugnis bedeuten, die Verschlüsselung für Millionen von österreichischen Verbrauchern zu untergraben und zu brechen.
„Jeder Versuch, die Verschlüsselung für einige ausgewählte Personen zu brechen, gefährdet gleichzeitig die Privatsphäre von Millionen von Österreichern. Dies ist weniger eine Frage der angemessenen Polizeibefugnisse als vielmehr eine Frage der technischen und sicherheitsrelevanten Aspekte. Schwächere Verschlüsselung macht österreichische Nutzer weniger sicher“ sagte Ossowski.
„Verschlüsselungsstandards von Apps wie Signal, WhatsApp und sogar iMessage aufzuheben, würde der österreichischen Regierung außergewöhnliche Befugnisse einräumen, die das Risiko bergen, jede und alle Kommunikation zu kompromittieren, nicht nur die von Verdächtigen oder Terroristen.
„Um gegen kriminelle Akteure vorzugehen, sollte die Koalition das bestehende Justizsystem nutzen, um Haftbefehle auf Grundlage eines begründeten Verdachts durchzusetzen, anstatt Messaging-Dienste und Apps dazu zu zwingen, diese Aufgabe für sie zu übernehmen“ erklärte Ossowski.
Das Consumer Choice Center weist darauf hin, dass ähnliche Versuche, die Verschlüsselung mit polizeilicher Gewalt zu brechen, bereits im Vereinigten Königreich und in Frankreich unternommen wurden, wo sie von Bürgerrechtsgruppen abgelehnt wurden.
###
Das Consumer Choice Center ist eine unabhängige, parteiunabhängige Verbraucherorganisation, die die Vorteile von Wahlfreiheit, Innovation und Wachstum im Alltagsleben für Verbraucher in über 100 Ländern fördert. Wir interessieren uns insbesondere für regulatorische Trends in Washington, Brüssel, Wien, Berlin, Ottawa, Brasília, London und Genf genau.
Erfahren Sie mehr auf consumerchoicecenter.org
-
 @ df67f9a7:2d4fc200
2025-04-09 04:42:34
@ df67f9a7:2d4fc200
2025-04-09 04:42:34Businesses want Nostr, but Nostr is not ready for business. What can be done?
- Businesses want reliable SEO and socials to put their brands in front of users, rather than arbitrary gate keepers, censoring the marketplace on a whim.
- Businesses want open access to harvest public data for free on a soveregnty respecting network, rather than paying gate keepers for access to user data of questionalble origin.
- Businesses want the freedom to NOT take ownership of certain user data collected by their apps, rather than being liabile for moderation and safe handling on their private infrastructure.
- Busineses want a single open protocol on which to build their apps, with unlimited potential and a diversity of shared users from other apps, rather than multiple siloed networks with difering APIs and demographics.
- Businesses want to own the technology they build and to use it as they wish, rather than submit their code for approval and control by arbitrary gate keepers.
But Nostr is not ready for business.
- Businesses DON'T want proprietary app data stored publicly as signed Nostr events on user specified relays.
- Businesses DON'T want to have to specify, or be constrained by, or even navigate the complexity of Nostr NIP standards for every novel kind of content that their apps generate.
- Businesses DON'T want to "open source" their entire suite of native apps JUST to assure end users that Nostr private keys are being safely handled.
- Businesses DON'T want to have to "rewrite" their entire app backend just to accomodate the Nostr way of "users sign events but dont actually login to your server" auth architecture.
- Businesses DONT want to suffer DDOS from bots and bad actors, or to expose their users to unwanted content, or even to have their own content disappear a sea of spam and misinformation.
Here is some of what can be done.
- More tools and services for private business apps to coexist with freedom tech, and even thrive together, on the Nostr network.
- Extensible Webs of Trust algos for discovery and reach into any audience or demographic of trusted users.
- WoT powered standard APIs for exposing content to Nostr (and other business apps) from within a “black box” business app.
- HTTP AUTH (NIP 98) integration for business apps, allowing users to create local content WITHOUT needing discrete signatures or “linked” user accounts.
- Frost compatible “login“ for business apps, allowing users to paste “disposable” nsecs into proprietary clients without fear of their “cold” nsec being compromised.
- Support for “incremental” (and voluntary) adoption of freedom tech into existing business apps, with easy off-ramps for businesses to transfer more and more siloed data onto the “public” network.
Thoughts so far…
-
 @ f7f4e308:b44d67f4
2025-04-09 02:12:18
@ f7f4e308:b44d67f4
2025-04-09 02:12:18https://sns-video-hw.xhscdn.com/stream/1/110/258/01e7ec7be81a85850103700195f3c4ba45_258.mp4
-
 @ 502ab02a:a2860397
2025-04-09 02:08:12
@ 502ab02a:a2860397
2025-04-09 02:08:12ทอดมันปลาฉลาด ของอร่อยและโภชนาการดี ที่หายากเพราะคนไม่ค่อยทำ เวลาพูดถึงทอดมันปลา ภาพที่ลอยมาในหัวของหลายคนคงเป็นเนื้อปลาเด้ง ๆ รสเผ็ดนิด หอมใบมะกรูดหน่อย ทอดให้ขอบกรอบนิด ๆ กินร้อน ๆ กับน้ำจิ้มหวานเปรี้ยว ถ้าไปถามว่าทำจากปลาอะไร ส่วนใหญ่ก็คงตอบว่า "ปลากราย" ซึ่งก็ไม่แปลก เพราะปลากรายถือเป็นวัตถุดิบยอดนิยมสำหรับทอดมันมายาวนาน
แต่วันนี้ เราอยากชวนมาทำความรู้จักกับอีกหนึ่งตัวเลือกที่น่าสนใจ…ปลาที่ชื่อออกจะขี้เล่นหน่อย ๆ ว่า “ปลาฉลาด”
ปลาฉลาดเป็นปลาน้ำจืดที่คนพื้นที่รู้ดีว่าเนื้อแน่น รสหวานธรรมชาติ และมีกลิ่นคาวน้อยจนบางคนเปรียบว่า "ขูดแล้วแทบไม่ต้องปรุงอะไรเยอะก็หอม" แถมยังมีเนื้อที่เหนียวในแบบธรรมชาติ โดยไม่ต้องใส่แป้งเพิ่มให้เสีย texture เลยแม้แต่น้อย
ความน่าสนใจของทอดมันปลาฉลาดคือมันให้สัมผัสที่ดีมาก Real food แท้ๆเพราะเนื้อปลาฉลาดเหนียวด้วยตัวเอง ไม่ต้องพึ่งแป้งหรือสารช่วยคงตัวใดๆ และยังมีกลิ่นหอมแบบปลาแม่น้ำที่ไม่ฉุน ไม่คาวดิน ไม่รบกวนสมาธิการกิน
เวลาขูดเนื้อปลาฉลาด จะรู้สึกได้เลยว่าเนื้อมัน "มีชีวิตชีวา" คือไม่ใช่เนื้อนิ่มเปื่อย ยุ่ย หรือแห้งจนฝืดมือ แต่จะมีความแน่น นุ่ม และติดยางนิด ๆ พอเอาไปคลุกกับพริกแกงกระชายสดสักนิด ใบมะกรูดฝอยบาง ๆ สิ่งที่เราทำแตกต่างเล็กน้อยคือ ใช้ถั่วพลูแทนถั่วฝักยาว ตีไปเรื่อย ๆ จนเหนียวได้ที่ แล้วทอดบนไฟกลาง ๆ...เสียงฉ่าแรกที่ลงกระทะ จะมาพร้อมกลิ่นหอมที่เรียกคนทั้งบ้านให้เดินมาด้อม ๆ มอง ๆ ได้แบบไม่ต้องใช้คำโฆษณา
ในแง่โภชนาการ ปลาฉลาดให้โปรตีนสูง ไขมันต่ำ และที่สำคัญคือ ย่อยง่าย ไม่หนักท้อง เหมาะสำหรับคนที่อยากกินของทอดแต่ไม่อยากให้ร่างกายต้องทำงานหนักเกินไป แถมยังนำมาประยุกต์เป็นทอดมันสายโลว์คาร์บได้สบาย ๆ เพราะเนื้อปลายึดเกาะตัวได้เองโดยธรรมชาติความดีงามของเนื้อปลา โดยไม่ต้องเติมแป้งหรือแปรรูปอะไรเพิ่มเติมอีก
แม้ปลาฉลาดอาจไม่ได้หาซื้อสะดวกเท่าปลาที่เลี้ยงในระบบฟาร์มทั่วไป แต่นั่นแหละคือเสน่ห์ของมัน…มันคือวัตถุดิบที่พาเรา “กลับไปหาของจริง” ที่ธรรมชาติให้มา ไม่ต้องปรุงแต่งมากก็อร่อย
ไม่ต้องบอกว่าปลากรายดีหรือไม่ดี เพราะมันก็ดีในแบบของมัน แต่ถ้าวันใดคุณอยากลองเปิดใจให้กับของหายากอีกหนึ่งชนิด…ลองทอดมันปลาฉลาดดูสักครั้ง แล้วคุณจะเข้าใจว่า บางครั้ง ของที่ไม่ค่อยมีคนพูดถึง อาจเป็นของที่ “พูดแทนตัวเอง” ได้ดีที่สุด #siripun #ตำรับเอ๋
-
 @ c230edd3:8ad4a712
2025-04-09 00:33:31
@ c230edd3:8ad4a712
2025-04-09 00:33:31Chef's notes
I found this recipe a couple years ago and have been addicted to it since. Its incredibly easy, and cheap to prep. Freeze the sausage in flat, single serving portions. That way it can be cooked from frozen for a fast, flavorful, and healthy lunch or dinner. I took inspiration from the video that contained this recipe, and almost always pan fry the frozen sausage with some baby broccoli. The steam cooks the broccoli and the fats from the sausage help it to sear, while infusing the vibrant flavors. Serve with some rice, if desired. I often use serrano peppers, due to limited produce availability. They work well for a little heat and nice flavor that is not overpowering.
Details
- ⏲️ Prep time: 25 min
- 🍳 Cook time: 15 min (only needed if cooking at time of prep)
- 🍽️ Servings: 10
Ingredients
- 4 lbs ground pork
- 12-15 cloves garlic, minced
- 6 Thai or Serrano peppers, rough chopped
- 1/4 c. lime juice
- 4 Tbsp fish sauce
- 1 Tbsp brown sugar
- 1/2 c. chopped cilantro
Directions
- Mix all ingredients in a large bowl.
- Portion and freeze, as desired.
- Sautè frozen portions in hot frying pan, with broccoli or other fresh veggies.
- Serve with rice or alone.
-
 @ b099870e:f3ba8f5d
2025-04-08 23:22:24
@ b099870e:f3ba8f5d
2025-04-08 23:22:24A donkey that is tied to a post by a rope will keep walking around the post is an attempt to free it self,only to become more immobilize and attached to the post.
ikigai
-
 @ e968e50b:db2a803a
2025-04-08 21:38:41
@ e968e50b:db2a803a
2025-04-08 21:38:41Hey stackers! Any y'all got a clue where I'm supposed to plug this in if I'm using Umbrel OS? I ssh into the machine, and everywhere I turn, it says that the file I'm trying to modify doesn't exist.
originally posted at https://stacker.news/items/938503
-
 @ 4d41a7cb:7d3633cc
2025-04-08 20:45:34
@ 4d41a7cb:7d3633cc
2025-04-08 20:45:34The most interesting relation that a lawyer holds to the community, outside of his technical occupation, is that of a legislator. Lawyers were the chief authors of the Constitution of the United States and of all the state constitutions.
It seems natural that lawyers should predominate in the government. They framed the former instrument. They both make and interpret the law.
Every time the text is in italics, it is a direct quote from the book.
Lawyers control every branch of the republican form of government: legislative, executive, and judicial. The influence of the lawyers is enormous, for good or for evil.

The lawyer has the supreme power of direction in the general exercise, commencement, and conduct of litigated or other legal matters. It lies with him to suggest and to direct. There is no arbiter over him but his conscience.
The duty of a lawyer is threefold: to the state, as an officer and citizen; to the court, as an officer and adviser; and to his client, as a fiduciary.
The crude sentiments of the people must be filtered through the lawyers, first as politicians, then as legislators, and afterwards as lawyers and judges.
Since lawyers are in charge of every government branch as ‘elected officials’ in representation of the people, education about morality and their duties and responsibilities is fundamental since in their hands lies the monopoly of violence held by the government.
Without contingent arrangements with lawyers, their power would become oppressive and tyrannical.
THE PROBLEM
“Permit me to issue and control the currency of a nation, and I care not who makes its laws.” Mayer Amschel Rothschild (1744-1812)
- Money was placed above rightness, truth, and justice. The incentive structure is inverted, and it's detrimental. Society is morally bankrupt above and below. Institutions are no better than the individuals who compose them.
- Common law was replaced by commercial code (encryption). Adding complexity, inefficiencies, costs, and capacity to trick and twist the law. The incentive structure is broken. Cheating pays more than playing clean; we have more lawyers but less justice.
- The lawyer is not educated about the spirit of the profession, his duty, and the form of government he’s supposed to protect. The interest of the client is put above the interest of the court and the nation. Jurisprudence is taught instead of elementary law.
INSTITUTIONS CANNOT BE BETTER THAN THE MEMBERS OF WHICH THEY ARE COMPOSED. THE GOVERNMENT IS NO DIFFERENT.
The combined acts of a body of lawyers, oft repeated, like an army of worms, silently and secretly gnawing at the foundation of a great and magnificent structure, will gradually but surely cause it to give way and tumble into ruins. It is perhaps not going too far to assert that the lawyers, as a class, are largely answerable for the minimum of respect and obedience that the public has for the law.
1. Money was placed above rightness, truth, and justice.
Commercialism and materialism have placed money above everything else, including the human. This has completely demoralized society in every aspect, from government and justice to education, architecture, medicine, nutrition, and so on.
This has a common denominator: the quality of the currency. As the quality of the currency evaporates, so does the values of the people. But money and currency are inanimate and dead objects; the real actors are the humans trading and using that money.
The ‘fiat money’ we use these days is a result of codified law, a legal fiction for money, a commercial contract paper to exchange goods and services, and a creature of the codified public and private law.
This fiat currency has enabled its possessors to buy, or secure, political and social positions, which should be attained only by real merit, refinement, and learning.
Today judicial systems do not provide justice, newspapers and mainstream media do not provide the truth, today banks do not protect your money, today medical treatment does not cure you, etc. Profit is placed above everything else.
It was evident that materialism completely controlled the economic structure, the ultimate goal of which was for the individual to become part of a system that provided him with economic security at the expense of his soul, mind, and body.
Manly P. Hall, 1988
Society was morally bankrupted by materialistic ideologies and human institutions that are no better than the individuals who compose them.
No judicial action can be put in motion without the sanction of some lawyer.
The lawyer appears everywhere and in all stages of business transactions but also in family and other private and delicate matters as the trusted advisor and friend of his client.
There is a moral corruption, equally as bad in its results upon the judges, the bar, and the community.
2. The incentive structure is inverted, and it's detrimental.
Moral relativism justifies every wrongdoing since ‘there’s no objective difference between right and wrong.’ How can you have justice if you can justify every wrongdoing and there’s no moral compass?
But if being a member of a club or friends with the judge gives you an edge, how can you have excellence, meritocracy, and justice? The incentive is to short-cup your way, to cheat, to manipulate the game and law to your advantage to get economic stability.
If you want to have justice and great institutions, you need to educate their members in a high level of morality, ethics, and purpose…
The commercial code replaced common law. The difference between a common-law lawyer and the practitioner under the Code is the difference between a surgeon and a butcher.
Codification has produced more material to aid dishonest clients than the common law supplied. The lawyers as a body are morally worse than their professional ancestors. The lawyers of the past believed the constitution was adaptable; those of the present regard it as elastic.
Laws have accumulated really fast, creating inextricable confusion and doubt. Making justice was turned into a thing of doubt and change.
Instead of seeking the truth, the courts and the bar are engaged in the pursuit of technicality and form.
A precedent can be found on any side of any subject that anyone chooses to espouse.
The ratio of lawyers has multiplied four times since the law was codified and its complexity increased. The code was adopted in New York in 1848. Argentina's Commercial Code was first adopted by the Province of Buenos Aires in 1859 and later as the national code in 1862. In 1850 there was 1 lawyer per 1000 citizens in the United States. Now there is 1 in 256.
The excessive number of lawyers is detrimental, both to the community and the morale of the profession.
It creates, encourages, and continues illegal, unfounded, and fraudulent practices, demands, and litigations, because necessarily many of the lawyers depend not upon professional knowledge and accomplishments but upon sharpness and cunning. In the effort to sustain themselves, much unnecessary and unfounded litigation is inaugurated, and many disgraceful practices are engendered.
Let anyone consider the effect of the forty or fifty thousand legal agents spending their lives distorting and prostituting the forms of justice, misapplying and perverting its principles, and undermining the constitution and laws, and they can make a fairly accurate calculation as to the longevity of the system of government under which they exist and thrive.
Cunning and trickery have replaced real knowledge and ethics.
The modern code lawyer knows little of elementary law, but he carries, as a soldier would a knapsack, a memory filled with sections of codes and adjudicated cases.
Sheltered in the grip of his office, the lawyer can always, insidiously and secretly, deflect the course of justice and defraud the law. It is difficult to detect him; he is representing another’s interest and is not responsible for his client’s morals or frauds.
To say nothing of the extra cost and expenses, the manifold delays and intricacies of legal procedure, the attempt to simplify has been to muddle, confound, and destroy—to produce a race of pygmy lawyers, chattering and quarreling over the meaning of words in the Code.
The ones who benefit from codification are the same ones who benefit from fiat currencies and central banks. They have used the same strategy in both cases: create a problem, manipulate public opinion and make them demand the ‘solution’ they have already prepared—codification of law, central banks, etc. Time has shown that the public was manipulated and that the solutions that was sold to them only increased the size of the problem they were ‘trying’ to fix.
Picture the lawyers training themselves in a school of dishonesty, trickery, and chicanery, diverting and stopping the machinery of the law, prostituting the forms of justice for gain, selling their knowledge, ability, experience, and such talent as they may possess to the client who pays most for the service, and resorting to every device of cunning and deceit to gain their end! Do such lawyers exist? Do such practices prevail? Unfortunately, yes. In the first rank of the profession can be found many lawyers whose services are sought only to enable guilty men to escape punishment; only to open a door for others to avoid the consequences of the civil law and of their contracts; only to defeat and evade the legislative will and public policy; only to show their clients how to cheat, defraud, vilify, and defame without penalty or damage.
His profession consists of thwarting the law instead of enforcing it. The modern idea of a great lawyer is one who can most successfully manipulate the law and the facts. The public no longer calls them “great” but “successful” lawyers. Not a great jurist or profound student, but a successful practitioner.
The more desperate the case he wins, the greater his reputation.
It is the common belief, inside and outside of the profession, that the most brilliant and learned of the lawyers are employed to defeat or strangle justice.
In this view, every lawyer might be regarded as an intellectual prostitute whose mind, time, experience, knowledge, and influence can be hired and occupied by any stranger who desires to comply with his terms as to fees.
There is nothing secret or underhand about this part of the lawyer’s business. It has the approval of the people everywhere.
In fact, the community looks with perfect complacency and composure upon a transaction in which the leading lawyer sells his talent, his knowledge, his time, and his influence to the most corrupt or infamous individual in the land.
The lawyer is deliberately made an instrument to thwart the law and justice—and he knows it.
He uses the machinery of the law to accomplish results contrary to justice, truth, and right.
When the laws can be easily thwarted, the moral sense of the whole community is deadened. The incentive for justice was inverted and destroyed.
3. The lawyer is not educated about the spirit of the profession.
The lawyer’s power arises from the necessity of political organization; he is the official and authorized agent that puts in motion the machinery of the law.
In the commencement of suits, the lawyer has need, therefore, of honesty, learning, prudence, and patriotism. It rests with him to preserve the purity of the legal system; to separate the chaff of fraud, exaggeration, and doubt from the wheat of fact and truth.
The government exists for the people, not the people for the government.
American governments were organized by the people to provide the people a peaceful way of resolving conflicts and trading peacefully, providing justice and the protection of private property and equality under the law. The public is taxed for the general expenses of the courts, among other things.
Here’s the secret, -the cornerstone- of all legislation.
The goal is to have an easy and understandable set of rules that everyone can understand: to make as few laws as possible; for, in all normal and sound conditions of society, that country is best governed which is least governed. But codification has done the opposite: add complexity and create thousands of codified laws.
Here’s the secret, -the cornerstone- of all legislation.
 The legislator should, therefore, be a man who understands the origin and nature of society- familiar with past and existing laws and history- with such practical and discriminating judgment as enables him to comprehend the wants and necessities of his fellow men.
The legislator should, therefore, be a man who understands the origin and nature of society- familiar with past and existing laws and history- with such practical and discriminating judgment as enables him to comprehend the wants and necessities of his fellow men.Still, none of the formal oaths defines the duties of the lawyer.
Everything is now left to the moral perception of the lawyer.
THE LOYALTY TO ITS CLIENT (THE HAND THAT FEEDS HIS MOUTH) IS PLACED ABOVE THE ALLIANCE TO THE STATE (THE HAND THAT FEEDS THE JUDICIAL SYSTEM).
It is not the exception, but the rule, for the lawyer to surrender his whole mental, intellectual, and physical power to his client’s cause.
REMEDY
To produce lawyers who can perform their duties, they should be taught to cultivate a moral sense; the nature and object of law; the nature and duties of citizenship; the nature and duties of a legislator; but above and beyond everything else, they should be taught the real mission of the lawyer - which includes professional ethics. These fundamental requisites to the making of a full lawyer are almost entirely overlooked in all of the courses of education followed in law offices, law schools, and academies or colleges. Lawyers are made up to be mere instruments for their clients, without any attention being paid to their duties to the State. The fact is extraordinary, nay, incredible. But it is true. The curriculum of legal study is based upon codification. O means the sentiment of codification., pervades and influences all legal education.
If the moral sense of the community, which is another name for public opinion, should be maintained to the highest possible degree, an educated Bar, and a free, pure and intelligent Press, are the factors which can do much to accomplish all these results.
But this conscience, which should guide the lawyer, comes from training and education.
Trained in the knowledge of human nature, when he enters the field of jurisprudence and politics, his acts and opinions should be of the greatest value to the people. I would build up a race of pure lawyers, as far removed from commercialism as possible.
The country needs such a class more than ever.
-
 @ 6be5cc06:5259daf0
2025-04-08 19:45:10
@ 6be5cc06:5259daf0
2025-04-08 19:45:10O que são os juros?
Os juros são um reflexo da preferência temporal dos indivíduos: o valor que damos ao consumo no presente em comparação ao consumo no futuro. Em termos práticos, se alguém te pede dinheiro emprestado hoje e promete devolver só daqui a um ano, faz sentido você querer algo em troca por ter que esperar e postergar o consumo — esse “algo a mais” é o juro.
Nas palavras da Escola Austríaca, os juros não são um fenômeno artificial ou técnico, mas sim um fato da realidade humana: tempo tem valor. E como o tempo passa para todos, a preferência temporal é um traço universal. Logo, juros sempre existirão — e isso independe de moeda, bancos ou qualquer arranjo institucional.
Juros e poupança
Num mercado genuinamente livre, os juros emergem da relação entre dois grupos:
-
Poupadores, que abrem mão do consumo presente para acumular bens que serão utilizados no futuro.
-
Investidores, que tomam emprestados esses recursos para realizar projetos que renderão frutos adiante.
Quando há muita poupança, a taxa de juros tende a cair, pois há mais capital disponível para investimentos. Quando há pouca poupança, os juros sobem, pois o capital é escasso. Simples assim. É uma dinâmica voluntária, descentralizada e natural — e, portanto, intolerável para os engenheiros sociais e planejadores centrais.
Como sabotar tudo
O problema começa quando uma entidade com poder coercitivo — como um banco central, como o Federal Reserve (FED) — resolve interferir nesse processo natural. Em vez de permitir que os juros sejam determinados pelas preferências temporais das pessoas, o FED manipula a taxa básica de juros da economia, criando a ilusão de que há mais poupança do que realmente existe.
Como ele faz isso?
Simples: imprimindo dinheiro do nada e injetando esse capital nos mercados financeiros por meio da compra de títulos, operações com bancos e linhas de crédito. Essa expansão monetária distorce os sinais econômicos: os juros caem artificialmente, mesmo sem um aumento real na poupança. O crédito se torna barato — mas ilusoriamente.
O efeito prático dessa mentira monetária
Empresas e investidores, enganados por esses juros baixos, começam a empreender projetos de longo prazo como se houvesse capital real disponível para sustentá-los. Shoppings, fábricas, startups, construções, tudo parece viável. A sensação é de prosperidade: mais empregos, salários, consumo e lucros.
Mas há um detalhe crucial: a preferência temporal da população não mudou. As pessoas continuam consumindo no presente — e não há bens de capital suficientes para suprir os dois desejos ao mesmo tempo: o consumo presente e os investimentos de longo prazo.
Com o tempo, a realidade bate à porta: os preços dos bens de capital sobem, os custos dos projetos disparam, os empréstimos se tornam mais caros e muitos empreendimentos tornam-se inviáveis. Então vem a quebradeira: demissões, falências e recessão. Todo o “crescimento” anterior se revela uma miragem inflacionária.
Ciclos econômicos: uma criação do Estado
Esse processo de boom artificial seguido de colapso inevitável é o que Mises e Hayek explicaram como o Ciclo Econômico Austríaco. Não é um “erro do mercado”. É o resultado direto da distorção dos sinais econômicos provocada pela manipulação dos juros. E o culpado tem nome: o banco central — neste caso, o FED.
O FED não é um árbitro neutro. Ele é um planejador central disfarçado de autoridade monetária. Seu objetivo real é manter o sistema financeiro vivo à base de impressora. Ele socializa prejuízos, distorce o cálculo econômico e destrói o processo de alocação racional de capital. Tudo isso enquanto afirma estar “estabilizando a economia”.
A consequência disso? Inflação, endividamento, má alocação de recursos e, acima de tudo, roubo institucionalizado da poupança das pessoas comuns. O juro baixo artificial é um imposto oculto. É uma forma disfarçada de pilhagem, uma transferência silenciosa de riqueza dos poupadores — que trabalharam e se abstiveram do consumo — para os primeiros recebedores do novo dinheiro, como bancos e governos. Essa manipulação é um confisco disfarçado, que destrói capital real e sabota o esforço honesto de quem poupa.
O caminho da correção
Para que os juros cumpram sua função genuína — sinalizar a escassez ou abundância de capital — é preciso eliminar a interferência coercitiva dos bancos centrais. Em um mercado verdadeiramente livre, sem manipulação monetária, os juros seriam determinados pela poupança real, e não por burocratas em Washington.
Isso exige o fim do monopólio estatal sobre a moeda. Exige a destruição da base legal que sustenta o cartel bancário. E exige uma transição para formas de dinheiro que não podem ser inflacionadas por decreto, como o ouro ou — melhor ainda — o Bitcoin.
Para finalizar
Os juros não são uma variável a ser “ajustada” por tecnocratas com PhDs. Eles são a expressão natural das escolhas humanas diante do tempo. Qualquer tentativa de manipular essa realidade só pode gerar desequilíbrios, crises e sofrimento econômico.
Enquanto o FED existir, ciclos econômicos serão inevitáveis. Não por causa do mercado — mas porque um punhado de burocratas acredita que sabe mais do que milhões de pessoas agindo voluntariamente.
Liberdade monetária é a única solução. E a destruição do banco central é apenas o começo.
-
-
 @ 8ba66f4c:59175b61
2025-04-08 18:19:43
@ 8ba66f4c:59175b61
2025-04-08 18:19:43👶 Je vais bientôt devenir papa.
Et ces derniers temps, une question me hante plus que je ne l’aurais cru : faut-il publier des photos de son enfant sur les réseaux sociaux ?C’est une réflexion que je n’avais jamais vraiment poussée avant.
Mais aujourd’hui, elle me semble incontournable. Parce qu’à l’ère des smartphones et des stories, poster devient un réflexe. On documente tout : les premières échographies, la chambre qu’on prépare, les petits vêtements, les premiers sourires… Et l’envie de partager est naturelle. C’est beau, c’est émouvant, on a envie de dire au monde qu’on est fier, qu’on est heureux.Mais voilà.
Plus j’y pense, plus je me dis que cette impulsion entre en tension avec d’autres principes qui me tiennent tout autant à cœur.D’abord, la question du consentement.
Mon enfant ne pourra pas me dire : « Je suis d’accord pour que tu postes cette photo ». Ni maintenant, ni dans quelques années quand les images auront déjà circulé. Il n’aura pas choisi de grandir avec une identité numérique créée pour lui, sans lui.
Ensuite, la protection de sa vie privée.
Une photo postée, même dans un cadre soi-disant « privé », peut être capturée, partagée, détournée, utilisée hors contexte. Il n’y a pas de bouton magique pour effacer ce qui est déjà parti sur les serveurs d’une plateforme.
Et aujourd’hui, il faut aussi parler de l’usage de ces images par les intelligences artificielles.
De nombreuses IA sont entraînées en partie à partir de données en ligne, y compris des photos. Ce qui signifie que le visage de mon enfant, s’il est mis en ligne, pourrait un jour se retrouver dans un dataset d’apprentissage, intégré à un modèle génératif, voire utilisé pour créer des deepfakes ou pour « entraîner » des applications que je n’ai jamais autorisées à le voir.
On ne parle plus seulement de vie privée. On parle d’exploitation, d’automatisation, de réutilisation potentiellement incontrôlable.Et puis, il y a la dimension éducative.
Quel exemple est-ce que je donne si je lui demande plus tard d’être prudent sur Internet, alors que moi-même j’aurais documenté toute son enfance en ligne, sans filtre ? Si je veux qu’il comprenne ce que veut dire « intimité », je dois sans doute commencer par la respecter dès ses premiers jours.
Ce n’est pas un jugement. Je comprends l’élan de publier, de partager, de célébrer.
Mais je crois que l’époque demande qu’on s’arrête deux secondes avant de poster. Et qu’on se demande :
– Pourquoi est-ce que je partage cette image ?
– À qui est-ce qu’elle appartient, au fond ?
– Et quel monde numérique je construis pour mon enfant, dès aujourd’hui ?Et vous, parents ou futurs parents, vous avez réfléchi à ça ? Vous partagez ? Vous vous retenez ?
Je serais curieux de lire vos retours. 🙏 -
 @ 8ba66f4c:59175b61
2025-04-08 18:03:53
@ 8ba66f4c:59175b61
2025-04-08 18:03:53Récemment, plusieurs membres du gouvernement ont évoqué cette possibilité : restreindre l’accès à certaines plateformes sociales en période de crise, pour limiter les débordements, les appels à la violence, ou les "fake news".
L'idée n'est pas présentée comme une censure, bien sûr. Plutôt comme une mesure "temporaire", "exceptionnelle", et "proportionnée".Mais en réalité, ce débat n’a rien d’anodin. Et il mérite une attention bien plus large que les quelques articles qui l’ont mentionné en marge de l’actualité.
Pourquoi ça pose (vraiment) problème ?
Parce que l’idée même de couper un réseau social, même temporairement, ouvre une brèche.
Un précédent.
Et dans l’histoire des démocraties modernes, les précédents deviennent vite des habitudes, surtout quand ils sont adossés à des notions floues comme "l’ordre public" ou "l’urgence".En France, comme dans l’Union européenne, les libertés de communication et d’expression sont des droits fondamentaux.
Et jusqu’ici, nous avons toujours critiqué – à juste titre – les pays qui bloquent Internet ou les réseaux sociaux :
- En Iran, en Inde, en Turquie, en Russie ou en Égypte.
- Pour des raisons souvent similaires : maintenir le calme, éviter la désinformation, empêcher la mobilisation.Mais dans les faits, ces coupures sont systématiquement utilisées pour neutraliser une contestation, contrôler un récit, ou empêcher la documentation de violences.
Et chaque fois, la presse française, les ONG, et les démocraties occidentales ont dénoncé ces actes.Alors que se passera-t-il le jour où la France appliquera ce qu'elle a longtemps dénoncé ?
La seule vraie solution, ce n’est pas plus de contrôle. C’est plus de résilience.
Face à cette dérive potentielle, des outils existent déjà.
Des protocoles pensés pour fonctionner sans autorité centrale, sans serveur unique, sans identifiant imposé.
Des réseaux impossibles à couper, à censurer, ou à faire taire d’un simple décret.Parmi eux, un nom commence à se faire une place : Nostr.
Pourquoi Nostr change la donne
Nostr, ce n’est pas une énième alternative à Twitter.
C’est un protocole minimaliste, décentralisé, libre.
Il permet à n’importe qui de publier, relayer, lire, sans dépendre d’une plateforme ou d’un serveur.✅ Identité basée sur une clé publique : pas besoin de mail, ni de téléphone.
✅ Données signées cryptographiquement : pas de falsification, pas de shadowban.
✅ Clients multiples, relays multiples, aucune infrastructure unique à cibler.
✅ Modération décentralisée : chacun décide ce qu’il veut voir ou pas.
✅ Possibilité de tourner sur Tor, en local, ou même de publier via satellite ou ondes radio si besoin.C’est simple : il n’existe aucun “bouton rouge” pour éteindre Nostr.
Et c’est précisément ce qui en fait un outil de liberté, et pas seulement un réseau social.En 2025, nous ne devrions pas avoir à nous préparer à contourner la censure.
Mais si même les démocraties commencent à l’envisager comme une option “raisonnable”, alors il est plus que temps de se poser les bonnes questions.
Et de s’outiller.Curieux de savoir qui ici a déjà testé Nostr ?
Utilisez-vous des clients comme Amethyst, Damus, Iris, Snort ou autre ?
Est-ce que vous y voyez un futur solide pour des communications libres ? -
 @ fbf0e434:e1be6a39
2025-04-08 15:08:21
@ fbf0e434:e1be6a39
2025-04-08 15:08:21Hackathon 概览
ETHiopia x BAM Hackathon 于 2 月 10 日至 14 日在线上进行,吸引了 108 名注册开发者和创新者深入探索以太坊技术。活动包括 Solidity 开发的技术研讨会和鼓励创造性技能培养的环节,最终审核通过了 38 个的项目。这些项目展示了参赛者的技术创造力以及他们对区块链技术的投入。
Hackathon 促进了以太坊生态系统内解决方案的创建,重点关注社区贡献和在现实场景中创新应用。参赛者在获得技能和探索了区块链创新的同时,也建立了开发者网络。活动提供了 2,000 美元 USDC 现金奖金,用于激励在代码质量、社区参与和展示技能方面表现出色的项目。
包括 ETHiopia, BAM 和 THE MU 在内的实体促进了非洲 Web3 BUIDLer的环境,推动了有影响力的解决方案。此次合作强调了区块链在应对现实世界挑战中的角色,并赋能了非洲开发者和BUIDLer。
Hackathon 获奖者
ETHiopia X Circles 奖项获奖者
第一名: Ethera
Ethera支持非洲内容创作者通过区块链实现货币化,利用Circles Protocol和CRC代币进行交易,以确保在Gnosis Chain上的透明度和去中心化。它通过Circles Protocol Avatar验证用户身份。
第二名: ETHqub
ETHiopia x BAM 一般Hackathon 获奖者
第一名: Imara
Imara是一个去中心化平台,帮助区块链开发者组建团队。它利用基于里程碑的质押和治理工具来增强协作,防止项目被遗弃,旨在区块链生态系统内实现广泛的集成。
第二名: Hakiba
Hakiba是一个去中心化的借贷协议,促进区块链上的社区信贷。它实施质押、担保和链上保险,以促进负责任的贷款和借款人支持,使用Solidity智能合约和FastAPI。
第三名: ETHqub
有关所有项目的更多信息,请访问 https://dorahacks.io/hackathon/ethiopiabamhackathon/buidl
关于组织者
BAM
BAM,即Bold African Movement,是一个为非洲的新兴建设者和创始人提供平台的机构,专注于区块链、AI和其他新兴技术。该组织致力于在非洲大陆培养创新人才,开发关键技术解决方案。通过积极参与重要的技术领域,BAM促进了这些行业的成长和协作。他们的使命是赋予非洲新一代的技术领导者,从而推动从愿景想法到实际实施的过渡。更多信息请访问他们的网站 joinbam.xyz。
-
 @ fbf0e434:e1be6a39
2025-04-08 14:55:41
@ fbf0e434:e1be6a39
2025-04-08 14:55:41Hackathon 概览
ETH Oxford 2025 Hackathon 于2月7日至9日在牛津数学学院举办,吸引了大量的开发者的兴趣和参与。活动共有318名开发者注册,最终通过审核有142个项目。活动强调创新和合作,主要集中在以太坊区块链上,参与者通过demo视频和GitHub仓库展示了他们的作品。
Hackathon 于2月9日结束,开发者们通过 Demo 他们的项目来角逐最后的奖项。他们在创新同时,也解决了区块链领域的各个技术挑战。这次 Hackathon 还促进了社区互动和知识分享,带来了区块链开发社区的实质贡献。
Hackathon 获奖者
主赛道奖项获胜者
- 可编程密码学
- CallOrNothing:利用区块链的去中心化扑克游戏,确保无中心化的信任游戏。
- AI
- DeFi
- Quantum Enhanced Cross-chain Arbitrage:结合量子优化与DeFi协议在生态系统间进行盈利套利交易的机器人。
- 消费者领域
- FlareGate:一个去中心化的P2P平台,用于法币-加密货币交易,整合Flare网络的安全数据。
- GuessTheHuman:基于区块链的AI社交推理游戏,用于识别真人玩家。
- The Golden Key:针对老年用户的区块链基础防欺诈移动应用。
Flare 奖项获胜者
- 刻入式数据协议
- FlareGate:用于法币-加密货币传输的去中心化P2P平台。
- Kingdom of LagaFlare:一个NFT卡牌游戏,通过区块链提供公平游戏和独特卡牌收集。
- ProteinMango:使用ZKP的自动理赔的参数性地震保险。
- 外部数据源/跨链
- portent
- bump.artist:为艺术家代币和收入分享的DeFi平台。
- ProteinMango
- FlareInsure:使用现实世界数据为智能合约服务的区块链小额保险。
- Decentralised Zero:利用Flare的FDC进行信任、透明的赌注操作的平台。
Torus 奖项获胜者
- 去中心化记忆机构
- ZK memory Organ:利用零知识证明实现高安全性和高效性的数据存储解决方案。
- Torus Decentralised Memory:安全、容错数据存储的分布式数据库。
- Porous Torus:为Torus AI代理提供安全、高吞吐量的数据存储。
- TorBit:通过OrbitDB为Torus AI代理提供零信任记忆系统。
- Discord 社区洞察生成器
- Hivemind:一个使用LLM从Discord聊天生成反馈和协作洞察的工具。
- stbb:分析服务器消息生成主题/趋势报告的Discord机器人。
- discord community bot:用于每周服务器报告的AI驱动Discord分析。
- 加密推特辩论分析器
- DebateFi:分析和总结有关加密货币的推特辩论,以获得可行的见解。
- Oxford Kaggle Debaters:一个用于加密推特分析、影响力评分和内容优化的AI工具。
- DebateChain:通过情绪和声誉评分分析加密推特辩论的AI。
- Wildcard 挑战
- NewsCrypt:去中心化论坛,通过辩论分析提升客观新闻报道。
基于Mina平台构建应用的获胜者
- MinAES:整合AES加密到Mina的zk-native区块链中,实现使用零知识技术的安全应用。
- MINA Verify:在电路中实现BLS12-381签名的一个平台。
- Guantanabet:基于Mina的隐私预测市场,使用基于ZKP的匿名投注。
Avalanche 奖项获胜者
- 一等奖 ($2000)
- Swiish.cash:一个通过手机号码全球稳定币转账的移动解决方案,使用Avalanche。
- Smart Memorandum:为智能合约提供司法管辖区特定法律文件的工具。
- blindbird.ai:去中心化AI推理平台,用于安全的小额付款。
- AADC- AI Agent for DeFi & Cross-Chain Operations
- 二等奖 ($1500)
- AI-Powered DeFi Position Management Platform:为GMX DEX头寸管理提供自然语言界面。
- NovaTools:包括多链NLP机器人和数据分析在内的加密AI工具。
- 三等奖 ($800)
- Oxwell AI agent:通过自然语言资产管理进行跨链DeFi助手。
- Wired:通过NLP为BNB/AVAX资产管理提供跨链AI助手。
- DEFAI:为链上操作提供自然语言的AI驱动DeFi代理。
- NLWallet:配备NLP和账户抽象的机构加密钱包。
- helpi:Avalanche平台的社会项目捐赠,配有AI风险评估。
AirDAO 奖项获胜者
- GameFi DApp
DeSci World: NERDo 奖项
- DebateChain
- CrypTweep by RugPullCoin#42
- Project Lydia:通过AI分析检测不当行为的Discord机器人。
- bump.artist
- Flare-FL:用于安全AI模型训练的去中心化联邦学习。
Ripple 奖项获胜者
- 使用RLUSD构建的顶级消费者应用
- CoverMax:一个使用oracle触发条件自动赔付的去中心化保险协议。
- BlockInvest:现代投资互助系统,利用XRPL通过智能合约进行集体储蓄。
- PayCoin IC:支持XRPL的QR码支付的移动RLUSD钱包。
- 使用XRPL的DID、凭证和RLUSD功能的最佳去中心化身份解决方案
- XRPL Diploma Verify:一个使用DIDs在XRPL区块链上安全存储和验证文凭的网页平台。
- 最具创新性的XRPL集成
BNB 奖项获胜者
- 主奖
- NovaTools
- insr.finance:一个通过Venus Protocol提供稳定币保护同时进行收益的保险协议。
- 荣誉提名
- BNB Shield:利用TEEs和ZKPs进行PEP检测的去中心化AML系统。
- CloutDrop:用于KOL空投优化的数据驱动平台。
- AADC- AI Agent for DeFi & Cross-Chain Operations
- Greenfield奖
- ReviewChain:一个去中心化的同行评审系统,提升学术出版透明度和质量。
- 荣誉提名
Vyper 奖项获胜者
- 最佳使用Vyper Lang
- SecureStake:一个使用Vyper进行质押和多签名验证的安全交易令牌管理平台。
- Quantum Enhanced Cross-chain Arbitrage
- The Golden Key by Avalock
若要探索 ETH Oxford 2025 的所有项目,请访问 DoraHacks。
关于组织者
ETH Oxford
ETH Oxford 是一个以推动区块链技术和创新而闻名的组织。以其技术专长而著称,ETH Oxford 对去中心化系统和安全交易协议的发展做出了重大贡献。其参与的众多项目提升了区块链的效率和可及性。目前,ETH Oxford 强调合作研究和区块链的实际应用,解决复杂的现实世界挑战,展现了其对技术进步和行业领导力的承诺。
- 可编程密码学
-
 @ 7d33ba57:1b82db35
2025-04-08 14:34:59
@ 7d33ba57:1b82db35
2025-04-08 14:34:59Barcelona is a city that sizzles with creativity, blends beach life with bold architecture, and radiates Mediterranean energy. From Gaudí’s surreal masterpieces to the lively buzz of La Rambla and the golden sands of Barceloneta Beach, it's a place where every street feels like a gallery—and every evening invites a fiesta.
🌟 Top Things to Do in Barcelona
1️⃣ Sagrada Família
- Gaudí’s unfinished masterpiece and Barcelona’s iconic landmark
- A kaleidoscope of colorful stained glass, soaring columns, and symbolism
- Book tickets in advance—it gets busy for a reason
2️⃣ Park Güell
- A whimsical hilltop park filled with mosaics, dragons, and curves
- Explore the Monumental Zone and enjoy views over the city
- Like stepping into a dream—or a fairytale!

3️⃣ Stroll La Rambla & Explore the Gothic Quarter
- A lively pedestrian street with flower stalls, performers, and markets
- Wander into the Gothic Quarter (Barri Gòtic) for narrow alleys, Roman ruins, and hidden plazas
- Visit Plaça Reial for tapas and a good vibe
4️⃣ Casa Batlló & Casa Milà (La Pedrera)
- Two of Gaudí’s iconic modernist buildings on Passeig de Gràcia
- Casa Batlló looks like it’s made of bones and sea waves 🌊
- La Pedrera is all flowing stone and rooftop sculptures
5️⃣ Magic Fountain of Montjuïc
- Evening light & music shows (check schedule!)
- Combine it with a walk up Montjuïc for museums, parks, and castle views
6️⃣ Barceloneta Beach & Port Vell
- Chill on the beach or bike along the palm-lined promenade
- Great area for seafood, sangria, or sunset cocktails
- Stroll the harbor and check out the yachts at Port Vell

🍴 What to Eat in Barcelona
- Tapas – Patatas bravas, croquetas, pan con tomate
- Paella – Best enjoyed seaside, with seafood or mixed options
- Calçots (in season) – Grilled green onions with romesco sauce
- Crema catalana – Like crème brûlée, but with a Catalan twist
- Vermouth – A pre-lunch drink that's become trendy again 🍸
Try local markets like La Boqueria or cozy taverns in El Born for the full flavor.
🚇 Getting Around
- Metro & buses are fast and efficient – get a T-Casual card or Hola BCN pass
- Walk or rent a bike—many areas are super pedestrian-friendly
- Taxis & ride apps like Free Now are widely available
🎉 Extra Tips & Local Vibes
✅ Time your meals late – locals eat lunch at 2–3pm and dinner after 9pm
✅ Watch a Flamenco show, but choose authentic venues, not tourist traps
✅ Visit Bunkers del Carmel for one of the best panoramic sunset spots in the city
✅ Be aware of pickpockets in crowded areas (especially on La Rambla)
✅ If you love art: check out Museu Picasso and MACBA (modern art)

-
 @ 554ab6fe:c6cbc27e
2025-04-08 14:16:11
@ 554ab6fe:c6cbc27e
2025-04-08 14:16:11Throughout my inquiry into the science of meditation, I often ponder why meditation is not a part of our cultural norm. It is so ancient and beneficial, yet it is a lost art. Sure, it is still alive in regions such as India and Eastern Asia, yet even those cultures have become so engulfed by western culture that the dedicated practice of this art seems lost to the wayside. I began to think that the reason western philosophical tradition became more popular than eastern traditions was because one was easily transcribed into heritable texts.
All ancient cultures explored philosophical questions, attempting to unravel the mystery of reality. We all know of Plato, Socrates, and Aristotle, who wrote their ideas down into books that sparked a long lineage of philosophers and writings. The tradition of writing down the attempted understandings of reality contrasts with the East in some ways. The opening chapter in the Dao De Jing, the introductory book of Daoism written by Laozi (老子, laozi) in ancient China, states (老子, 1994):
The Tao that can be spoken is not the eternal Tao The name that can be named is not the eternal name The nameless is the origin of Heaven and Earth The named is the mother of myriad things Thus, constantly without desire, one observes its essence Constantly with desire, one observes its manifestations These two emerge together but differ in name The unity is said to be the mystery Mystery of mysteries, the door to all wondersDaoism involves mindfulness practices such as meditation and Qi Gong that cultivated a sense of understanding of reality through these practices. It is a philosophy that claims the understanding of reality, not through analytical thinking but meditation. Therefore, the wisdom achieved is not easily described in words, hence the poetic and cryptic nature of the Dao De Jing. In the East, the ideas are not easily transcribable, contrary to the West, indicating why modern society is dominated by western thought and not meditative practices because communities learn from our ancestors' writings. Westerners, in my mind, took a different route in understanding reality, or so I thought. My ideas changed when I read two fascinating books: The Immortality Key by Brain C. Muraresku and In the Dark Places of Wisdom by Peter Kingsley. These books argue that the ancient ancestors of the West sought wisdom through the same means as the ancestors of the East, and we have just forgotten.A defining trait of western thought is the use of logic to deduce the nature of reality. Before the time of Plato, there was an ancient Greek philosopher known as Parmenides. He is known as the discoverer of logic. In my mind, logic is not something discovered. Yet, the title given to Parmenides speaks volumes to his contributions to the foundations of Greek philosophy and culture.
Contrary to the philosophers who followed him, he did not write a book of ideas. Instead, he wrote a poem. A cryptic one, nonetheless providing a distinct similarity between Parmenides and Laozi. The cryptic nature of his poetry has led to much scrutiny by scholars. They seek to understand his ideas from an analytical point of view and fail to do so—a method of analysis expected from classicists. However, Peter Kingsley takes a perspective that is far more conducive to the poem's true intention. In his book, Kingsley describes Parmenides as an Iatromantis, a prophetic healer of sorts with ties to Apollo who practiced incubation (Kingsley, 1999). Incubation is where an individual would lay down (as if a corpse) in a cave for extended periods until they had a sort of dream where their body descended into the underworld then came back. This experience could be used as a form of healing (Apollo was also the god of medicine) and granted wisdom derived from the gods. The insight could be philosophical and applied to the creations of laws (Kingsley, 1999). Incubation was not only associated with Parmenides either but also with Pythagoras (Kingsley, 1999). Surprising is the stark similarities between meditation of the East and incubation of the West. It seems that culturally significant individuals from the ancient world, regardless of geographical location, used the same method to achieve great wisdom.
Incubation may not have been the only means by which the ancient Greeks sought to achieve the wisdom of the gods. In the book The Immortality Key, Muraresku argues that during the Eleusinian Mysteries, the ancient Greeks consumed a beer spiked with psychedelic chemicals possibly derived from ergot (Muraresku, 2020). The experience was a means of going into the underworld, dying before dying, and coming back with greater wisdom and immortality (Muraresku, 2020). Muraresku further argues that this tradition continued into the Christian age with wine and holy communion. In double-blind studies, psychedelics induce incredible life-changing spiritual experiences (Griffiths et al., 2006). Both meditation and psychedelics seem to deactivate certain brain areas within the Default Mode Network (Farb et al., 2007; Palhano-Fontes et al., 2015; Scheibner et al., 2017; Speth et al., 2016). It is easy to draw a plausible connection of psychedelics as biotechnology capable of inducing, if not temporarily, the experience achieved by meditation and incubation. This experience, which reaches an altered form of consciousness, grants a spiritual understanding of great insight. At least, the Greeks and Romans likely thought so.
In The Immortality Key, I learned that the Greeks had two words for the English "know." There is a Greek word that describes a more reflective, analytical, and logical form of knowing. Then there is "gnosis," which describes a more intuitive and experiential state of knowing (Muraresku, 2020). Plato, Socrates, Aristotle, their knowledge lies within the former, whereas Parmenides and Pythagoras were in the later "gnosis" camp. I suppose this dichotomy could be voiced in the difference between "knowledge" and "wisdom" in English. Ironically, we derived our word "know" from" gnosis." In this context, do we truly know much of anything?
When it comes to archeology, nothing is certain. I cannot claim that these researchers are correct. Nonetheless, it is common knowledge that many cultures across the ancient world used meditation and psychedelics for various spiritual and ceremonial purposes. It existed in China, Japan, India, the Toltec people of southern Mexico, the Amazon, and other places. Why would the foundational cultures of the western world be any different?
I remember learning that scholars point to the crusades as a pivotal moment that leads to the development of the Renaissance in Europe. The reason was that Europeans had lost connection to the writings of ancient Greek and Roman society during the last age. It wasn't until the Europeans invaded the Middle East, andacquired the texts from the great libraries there that a massive boom in cultural prosperity and development began. Perhaps we are due for another remembering.
References Farb, N. A. S., Segal, Z. v., Mayberg, H., Bean, J., Mckeon, D., Fatima, Z., & Anderson, A. K. (2007). Attending to the present: Mindfulness meditation reveals distinct neural modes of self-reference. Social Cognitive and Affective Neuroscience, 2(4), 313–322. https://doi.org/10.1093/scan/nsm030
Griffiths, R. R., Richards, W. A., McCann, U., & Jesse, R. (2006). Psilocybin can occasion mystical-type experiences having substantial and sustained personal meaning and spiritual significance. Psychopharmacology, 187(3), 268–283. https://doi.org/10.1007/s00213-006-0457-5
Kingsley, P. (1999). In the Dark Places of Wisdom (Seventh). The Golden Sufi Center.
Muraresku, B. C. (2020). The Immortality Key: The Secret History of the Religion With No Name. St Martin's Press.
Palhano-Fontes, F., Andrade, K. C., Tofoli, L. F., Jose, A. C. S., Crippa, A. S., Hallak, J. E. C., Ribeiro, S., & de Araujo, D. B. (2015). The psychedelic state induced by Ayahuasca modulates the activity and connectivity of the Default Mode Network. PLoS ONE, 10(2), 1–13. https://doi.org/10.1371/journal.pone.0118143
Scheibner, H. J., Bogler, C., Gleich, T., Haynes, J. D., & Bermpohl, F. (2017). Internal and external attention and the default mode network. NeuroImage, 148(January), 381–389. https://doi.org/10.1016/j.neuroimage.2017.01.044
Speth, J., Speth, C., Kaelen, M., Schloerscheidt, A. M., Feilding, A., Nutt, D. J., & Carhart-Harris, R. L. (2016). Decreased mental time travel to the past correlates with default-mode network disintegration under lysergic acid diethylamide. Journal of Psychopharmacology, 30(4), 344–353. https://doi.org/10.1177/0269881116628430
老子. (1994). 道德经 Translated by Derek Lin.
-
 @ 5188521b:008eb518
2025-04-08 13:33:42
@ 5188521b:008eb518
2025-04-08 13:33:42Ecology
When my father died, an entire ecosystem system of beneficiaries withered. Moussa Ag El Khir funded scholarships and community projects, paying thousands of Dinars monthly to stop the oasis town of In Salah from burning up. The few families we knew operating outside the oil-field economy would be forced to flee to the Mediterranean coast, along with just about every other Berber.
It wasn’t unexpected. My father had cystic fibrosis for all sixty-one years of his life. So far, that’s the only legacy he’s passed on to his children. My brothers are just carriers, but me, his precious daughter ended up like him in more ways than one.
We sat there in the lawyer’s office in Algiers, my brothers and I, staring at the ledger which contained payment for his life’s work.
“And he only left one word in his will?” asked Ibrahim for the third time. Ecology.
The lawyer said Moussa was very clear. He chose each of the keys himself. The contents of the ledger would belong to whoever could decode his life — those who understood the real meaning. Then he cut all communications and walked into the Sahara. The Tuareg caravan on the road to Akabli found his body a week later, reddened by sand burn.
Earth
We made an agreement that day. To share each word we discovered. We could break the code together. Of course, Ibrahim and Hama didn’t share anything. We barely speak. That’s what happens when one child follows their father into science, and her two brothers move to France the minute they get rich enough to buy a wife. I bet they spent longer looking into legal loopholes to get their hands on my father’s assets than they did trying to identify the keys.
That day was the start of my second life, and I went from research assistant at a regional university to private-key detective. 2048 words and few clues where to start. Although I was 27, I was virtually a grandmother according to the In Salah wives. But of course, I could never be a grandmother, or even a mother. Every night, I scoured photos in the family archive. An initial sweep of his digital footprint returned no out-of-place instances of any keywords.
It took me a year to find the GPS tag he’d added to one photo — an eighteen-year-old daughter standing next to a father proud of his first infinite solar prototype. The panel has long-since been torn out by the oil corp, but the base is still there. I drove the three kilometres from the town limit and shone the high beams at the spot. When I got out, the air was cool but still thick with sand. A few more steps through sinking dunes, and I saw it. He’d scratched a little globe into the blistered metal, and for a moment, my mucus-laden lungs tasted clear air.
Trigger
The next word took three years. Friends, contacts, professors, biographers — visits to anyone with whom he might have left a clue. But it was in the In Salah hospital, where, upon a routine CF checkup with Jerome Devailier, a French doctor, ‘trigger’ appeared. The government might stack everything against the desert peoples, but they hadn’t taken away healthcare. I’d been living off the kindness of neighbours while finishing my thesis on the very solar technology my father developed. How could he have known the ‘buyer’ was just a tendril of the very oil company he sought to defeat.
Dr Devalier went through the list of carcinogens and allergens to avoid with my new drugs. Over forty triggers which could be my downfall. If I was lucky, I’d live as long as my father did.
By then, my research stipend was long gone. I existed on toughened bread and soup, which always carried the taste of the scorched city air. Yet, I stayed. The public library, disconnected from the grid by the oil corp, was where I finished my manuscript. They would fight its publication. Since father’s money no longer flowed into the town, many had deserted me. There were those who said he killed an entire people by selling his solar patent to the wrong buyers. Others in In Salah worshipped his name, but eventually, they all trudged north to the cities. My brothers sold the family home from under me, forcing me to follow.
When I returned from the hospital, I dug out my father’s medical documents. On every page, the word ‘trigger’ was underlined. That was the moment I knew my life’s work would be unlocking the ledger, not publishing studies on long-dead solar panel technology. That battle was lost.
They
All we need is a simple document, but here, it is the administrators’ job to send people away. Physical copies are only issued in extreme circumstances. Citizens’ Registry screens played endless repetitions of how to apply for digital documents. The shrill voices of family members desperate for the original copy of a pirated document drowned the TV messaging. Women removed headscarves and revealed thick black hair; teenagers paced. The atmosphere thickened with sweat. And hours passed. Each appointment required a reset of digital protocol, biometric tests, and identity cards from legal descendents. Through counterfeit identities, our Dinars leak into the hands of criminals, but still the government denies the need for bitcoin. They just print more money. They is the word my father used for the government that fought his patent so hard.
After a four-hour wait, I discovered that the physical death certificate included an ‘identifying mark’ on the deceased’s body. The ink was fresh — etched into the shoulder blade of a man who wished to turn his back on the government that ignored its people. The tattoo read aqqalan, the Tamasheq word for they.
Scheme
It took two trips to his cluttered Marseille office to convince him I was serious. Two visas, two flights, and the small amount from the sale of the family house. But few detectives wanted to work for a promise.
The ledger could not legally be owned in Algeria, and Laurent Mercier was the only serious professional who entertained a percentage of what was on there. The solar tech patent and documents from my father were enough to start Laurent on the trail. ‘Preliminary,’ he said, until I had the ledger in my possession.
“Flying is not easy with my condition,” I said.
He lowered his sunglasses. “Working is not easy without money.”
Contact with my brother through the lawyer in Algiers was achingly slow, but eventually they agreed to give me possession. What was 33% of nothing anyway? Years had gone by.
So, when I sat for the second time, in the sweaty office in Marseille, I gave Laurent the ledger, and he handed me a surprise. In all his business affairs, my father used little English, but the word ‘scheme’ appeared in all three company names he incorporated in the last three years of his life. We had our fifth word, and I finally had someone on my side.
Make
Some days, I could barely walk to the public library. I became lethargic and mostly sat in the cool dark of my room in the shelter. The government refused to provide housing outside of Algiers, but a Tuareg organisation from Mali opened a shelter in In Salah. Bulging eyes and faded clothes stared back in the mirror each day. How long had it been since I’d been to a wedding, or celebrated a friend’s child? Occupants came and went, and all that was left was a barren room and one meal per day.
As the sun punished the city with every ray of Allah’s untapped gift, streets grew thick with dust, and the local government fell, seat by seat, to oil execs. The only transport running was to and from the oil fields, which belched the remnants of the land into the sky. And still they worked. Still they sat on my father’s patent and refused to supply the world with efficient solar power.
With little else to cling onto, I harboured thoughts of how I could spend the ledger money. Fixing the town and replanting lost gardens. Bringing people back. That all took a back seat to decoding the message my father was sending. Laurent and I began to believe that the keys he chose formed some sort of instruction for his legacy.
Ten years to the day after his death, I was in the public library, looking for clues in an English history book. On my exit, the librarian stopped me.
“We have a gift for you, Kana.”
I waited while he fetched a package.
“Your father instructed me to give this to you. But not before this date.”
My hands tore open the package. More books, technical manuals, and hand-written notes. Amongst the papers was a tasselled leather bookmark embossed with the four letters that comprised one of the seven missing words. Make.
Citizen
It’s hard for a father in Algeria to admit to his daughter that she is his spirit — the heir to his life’s work. Of course he felt terrible guilt after our mother’s passing. That was when the letters started.
Moussa wrote to himself really, trying to come to terms with bringing a protégé into the world with a bright scientific mind and lungs that would snap her life expectancy. We communicated by letter for the last few years of his life — sharing the breakthroughs of his findings and what it might mean for our decaying oasis town. Analogue writing was the only real privacy, he said. His letters always ran to the same length, as if they were one lesson divided into equal chunks. We even exchanged letters during his last hospitalisation in Algiers. Those words were the only real strength I gained.
It was Laurent who analysed the letters with a new text scanning tool. For me, my father’s last letters were advice, regret, pain, and love, but to Laurent, they were simply a puzzle to solve to get one step closer.
Our letters gave Laurent the idea to communicate via physical mail. The process was painful, with letters sent from outlying towns before being shipped across the Alboran Sea and up into France. Muatin was one name my father called me. Like him, I dreamed of helping many through science. This was one of the few Arabic words in the French letters he wrote. It was also the only keyword included in any of the letters. Citizen.
When
Years of quiet followed. In Salah became unlivable after they co-opted the city reservoir for cooling drilling rigs. Each study that proved the field was still viable funnelled funds away from the locals who clung on. Resettlement benefits went up, and all but the semi-nomadic Tuaregs left. I followed. My health could not take much more desert. In the cooler coastal plains, I recovered strength, and subsidies for new medications helped me survive on a meagre teaching salary.
With no further clues, my Marseillais detective lost interest. His last letter, sent years ago, stated with unusual brevity that he was resigning the case. No payment was due.
I had lost my health, my father, his work, my money, our house, the town, and I spent each week delivering science and English classes to teenagers. They had no more hope for our country than I had. Algerians had already lost the Sahara. A one-degree temperature shift each decade of my life had shrunk Africa and sent its peoples northwards.
My father’s word puzzle occupied my thoughts. The combinations and permutations of letters and characters had millions of possible meanings but only one correct answer. Yet simple linguistic logic provided the next word. The headteacher was a linguist — a profession long lost to the higher-powered text analysers and language AI. He spoke little English but asked about the categorisations of grammatical terms in the 2048 key words.
“Why do you ask?”
“Because,” he said, “for a sentence of twelve words, at least one conjunction is necessary to form a second clause.”
He was right. I had been focussing on lists and complex codes to build my father’s motto. When I got home, I furiously searched my list of terms for conjunctions. I found only one. ‘When.’
Can
The permutations were still huge. Even eliminating some of the more conceptual words did not help. Millions of sentences existed in my dead father’s mind. Millions of meanings, all lost to the need for more energy to fund the world’s great thirst for energy. Still, the panels in most of the ‘dead middle’ (as the space between the tropics became known) melted at over 50 degrees.
I was back in Paris for CF treatment. As a young woman, I would have been pleased to make fifty years. But the realities of daily visits and the sickness brought on by medication stung. I wanted things to end, even when I discovered the next key.
It had been years since I had dreamed of the freedoms my father’s fortune could bring. Parts of Asia held out against bitcoin, but the cost of countries doing business off-network had become prohibitive. Eventually, the fossil conglomerates would give in to the need for solar mining and the provision of universal energy.
It was in a Parisian hospital bed that I discovered ‘can.’ My wardmate, a rough labourer from Oran, found a biography in the hospital library that made me sit up straight. ‘Can’ was repeated in almost every description of my father in his one-time business partner’s book. And it was this Arabian ‘businessman,’ Abdulkarim Rahman, who brokered the deal that robbed the world of infinite solar power. Each page mocked my father as believing only physical impossibilities are impossible. He branded him the ‘can man.’
Drastic
During my recuperation, I spent the final two weeks of my visa stay in Marseille. My days passed with endless algorithm tweaks to reject or accept word orders for the elusive twelve-word sentence my father once wrote.
Food lost its taste, and friends and colleagues in academia had scattered. In-person meetings were often contained to the night hours, but Marseille was not a place to go out after dark. The latest protests had gotten violent, and the government looked likely to topple. My people had always been resilient, but when the option to move and operate a caravan was removed by General Hafiz, part of my spirit died. I resolved to spend my final years in In Salah, however uncomfortable they would be.
My final port of call before returning was Laurent’s office. The eTaxi cast me out into the dusty street, and I wheezed as I climbed the three flights of stairs to his tiny door on Rue Marché. We hadn’t spoken in years, but I was surprised to find a different name about the door. Pascale Dupont, Investigateur.
The assistant I remembered was quite the opposite to Laurent — slow and methodical, short and heavy set.
“Madame,” he said. “I have difficult news.”
Their business had always straddled the law, but I never imagined an ex-officer of the law could be convicted of treason.
“A closed-door trial,” said Pascale. Then he handed over an air-gapped 3D storage file. “Laurent knew you would come for this.”
My mind cast forward to the reams of information he must have built on my father. The patents and technical diagrams he illegally acquired and other clues. I instantly recognised the brand of storage file as a keyword. Drastic.
“How can I thank him?”
“He is dead, madame.” Pascale hung his head. “He survived prison for only two weeks.”
Must
My final years brought me home. In Salah had gained fame for its one group of Tuaregs who refused to leave. The Lakzis owned a house in a desperate condition, not dissimilar to my failing body. By the age of fifty-two, I could no longer walk, but they welcomed me. I pooled my disability allowance and some money I’d gained from selling my father’s watch. We waited for the world to mourn the death of a once great city. We would keep it alive by refusing to move, by refusing to permit its rebranding as an ‘industrial area.’ Now the oil fields were finally drying up, they wanted to dig under the town.
We had managed to eliminate half of the remaining words. Just under 1,000 possible selections for the final two words, but little idea of an order.
The problem was that I was the only English speaker among them, and it took great energy to attempt to teach the meaning of the words and possible grammatical constructions for my father’s sentence.
But soon, patterns began to emerge. Fragments of word pairings and groups. ‘Trigger drastic scheme’ appeared again and again in the permutations. ‘They can’ and ‘When they can’ gave a tantalising glimpse. We ranked sentences in terms of likelihood to form the full key and categorised them by the most likely remaining words. Due to the need for a modal verb, ‘must’ scored highest by our calculations.
In this race to unlock the ledger before In Salah’s destruction, we nosed ahead.
Yet the day of that discovery was my final day in the desert. An air ambulance transported my feeble body to Algiers, and I would never return.
They messaged me — so close. They would unlock the ledger with the final word after my operation. The bitcoin could undo the wrongs of the past, and my father’s sentence would live on.
End
The phrase which began the global revolution first appeared on the wall of a much-disputed oil refinery in the desert outside In Salah, Algeria.
When they can make ecology end, citizen earth must trigger drastic scheme
Soon, the graffiti marked government buildings in Algiers. Activists took to the streets. Governments crumbled and currencies collapsed. Climate groups received massive donations said to come from ‘the one,’ a ledger with a huge stack written off by financiers the world over. The codebreaker credited with unlocking the ledger was unable to witness the transfer of 10,000 coins to the Global Climate Fund due to her death, aged 52, from a congenital condition.
The words of Moussa Ag El Khir now mark each of the millions of panels, which line the ‘dead middle.’ They contribute over 80% of the Earth’s power supply.
To mark the fiftieth anniversary of his death, the World Climate Forum will be held in the town of his birth, In Salah, Algeria. This story, compiled from the diaries of his daughter, Kana Ult El Khir, will be read as the opening address of the conference.
This story was originally published in 21 Futures: Tales From the Timechain
To continue the story of the real-world treasure (sats) use the address (it's real).\ Who knows, maybe some zaps will find their way into the wallet...





































