-
 @ 86dfbe73:628cef55
2025-05-18 07:23:56
@ 86dfbe73:628cef55
2025-05-18 07:23:56Es gibt einen neuen Markt. Es ist der Markt der Aufmerksamkeit. Die Aufmerksamkeitsökonomie ist ein Markt, auf dem menschliche Aufmerksamkeit als knappes Gut gilt. Werbetreibende sind zunehmend auf der Suche nach ihr. Aber Vorsicht: Aufmerksamkeit ist nicht das Produkt, sondern das Zahlungsmittel. Wer hier seine Produkte (Informationen) feilbietet, darf froh sein, wenn er Aufmerksamkeit – und nur diese – findet.
Der Schlüssel zum Erfolg in diesem Markt besteht darin, unsere Aufmerksamkeit mit ansprechenden Inhalten zu fesseln, sie durch verschiedene psychologische Tricks und Manipulationen zu erhalten und unsere Gehirne für Werbedollar auszunutzen. Um einem Nutzer Werbung zeigen zu können, muß dieser sich allerdings auf der Plattform befinden. Daher wollen alle Dienste - ob FB, YouTube oder Amazon - Nutzer möglichst lange auf der eigenen Site oder eben App halten. Allerdings ist Aufmerksamkeit eine biologisch begrenzte Ressource, um die immer mehr Angebote konkurrieren.
Der unglückliche Nebeneffekt davon ist, dass diese Manipulationen unsere Fähigkeit, klar zu denken und logische Meinungen zu bilden, weiter beeinträchtigen. Während die verfügbare Zeit pro Tag konstant bleibt, nimmt der Wettbewerb um unsere Aufmerksamkeit exponentiell zu. Unter dem immensen Druck, Engagement und Wachstum in den Vordergrund zu stellen, haben die kommerziellen Plattformen einen Wettlauf um die Aufmerksamkeit der Menschen in Gang gesetzt, der unsichtbare Schäden für die Gesellschaft verursacht hat.
Der Internet-Nutzer hat heutzutage, mit den richtigen Tools, die Macht über seine kostbare Aufmerksamkeit und wird deswegen jede Werbung wegfiltern, er wird jedes Bezahlmodell unterlaufen, das sich ihm in den Weg stellt und er wird jeden Text aus seinem Kontext reißen und ihn einbetten in seinen eigenen Kontext.
Wir müssen Aufmerksamkeit als politische Kategorie bewerten. Die Beobachtung, dass Energie der Aufmerksamkeit folgt, gilt als Grundlage für politische Debatten und bestimmt das Bild von Öffentlichkeit. Welcher Meinungsäußerung wird öffentlich Aufmerksamkeit geschenkt und welche Meinungen läßt man privat an sich heran?
-
 @ 87f5e1d9:e251d8f4
2025-05-17 13:13:42
@ 87f5e1d9:e251d8f4
2025-05-17 13:13:42In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
Why Choose Crypt Recver? 🤔 🔑 Expertise You Can Trust At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases. Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds! Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets. Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security. Don’t Let Lost Crypto Ruin Your Day! 🕒 With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now! Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back! 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞 For quick queries or support, connect with us on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
 # Why Choose Crypt Recver? 🤔
# Why Choose Crypt Recver? 🤔🔑 Expertise You Can Trust\ At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process\ Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate\ With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure\ Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools\ We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
 # Our Recovery Services Include: 📈
# Our Recovery Services Include: 📈- Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds!
- Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets.
- Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security.
Don’t Let Lost Crypto Ruin Your Day! 🕒
With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now!\ Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back!\ 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞
For quick queries or support, connect with us on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 609f186c:0aa4e8af
2025-05-16 20:57:43
@ 609f186c:0aa4e8af
2025-05-16 20:57:43Google says that Android 16 is slated to feature an optional high security mode. Cool.
Advanced Protection has a bunch of requested features that address the kinds of threats we worry about.
It's the kind of 'turn this one thing on if you face elevated risk' that we've been asking for from Google.
And likely reflects some learning after Google watched Apple 's Lockdown Mode play out. I see a lot of value in this..
Here are some features I'm excited to see play out:
The Intrusion Logging feature is interesting & is going to impose substantial cost on attackers trying to hide evidence of exploitation. Logs get e2ee encrypted into the cloud. This one is spicy.
The Offline Lock, Inactivity Reboot & USB protection will frustrate non-consensual attempts to physically grab device data.

Memory Tagging Extension is going to make a lot of attack & exploitation categories harder.
2G Network Protection & disabling Auto-connect to insecure networks are going to address categories of threat from things like IMSI catchers & hostile WiFi.
I'm curious about some other features such as:
Spam & Scam detection: Google messages feature that suggests message content awareness and some kind of scanning.
Scam detection for Phone by Google is interesting & coming later. The way it is described suggests phone conversation awareness. This also addresses a different category of threat than the stuff above. I can see it addressing a whole category of bad things that regular users (& high risk ones too!) face. Will be curious how privacy is addressed or if this done purely locally. Getting messy: Friction points? I see Google thinking these through, but I'm going to add a potential concern: what will users do when they encounter friction? Will they turn this off & forget to re-enable? We've seen users turn off iOS Lockdown Mode when they run into friction for specific websites or, say, legacy WiFi. They then forget to turn it back on. And stay vulnerable.

Bottom line: users disabling Apple's Lockdown Mode for a temporary thing & leaving it off because they forget to turn it on happens a lot. This is a serious % of users in my experience...
And should be factored into design decisions for similar modes. I feel like a good balance is a 'snooze button' or equivalent so that users can disable all/some features for a brief few minute period to do something they need to do, and then auto re-enable.
Winding up:
I'm excited to see how Android Advanced Protection plays with high risk users' experiences. I'm also super curious whether the spam/scam detection features may also be helpful to more vulnerable users (think: aging seniors)...
Niche but important:
Some users, esp. those that migrated to security & privacy-focused Android distros because of because of the absence of such a feature are clear candidates for it... But they may also voice privacy concerns around some of the screening features. Clear communication from the Google Security / Android team will be key here.
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ c631e267:c2b78d3e
2025-05-16 18:40:18
@ c631e267:c2b78d3e
2025-05-16 18:40:18Die zwei mächtigsten Krieger sind Geduld und Zeit. \ Leo Tolstoi
Zum Wohle unserer Gesundheit, unserer Leistungsfähigkeit und letztlich unseres Glücks ist es wichtig, die eigene Energie bewusst zu pflegen. Das gilt umso mehr für an gesellschaftlichen Themen interessierte, selbstbewusste und kritisch denkende Menschen. Denn für deren Wahrnehmung und Wohlbefinden waren und sind die rasanten, krisen- und propagandagefüllten letzten Jahre in Absurdistan eine harte Probe.
Nur wer regelmäßig Kraft tankt und Wege findet, mit den Herausforderungen umzugehen, kann eine solche Tortur überstehen, emotionale Erschöpfung vermeiden und trotz allem zufrieden sein. Dazu müssen wir erkunden, was uns Energie gibt und was sie uns raubt. Durch Selbstreflexion und Achtsamkeit finden wir sicher Dinge, die uns erfreuen und inspirieren, und andere, die uns eher stressen und belasten.
Die eigene Energie ist eng mit unserer körperlichen und mentalen Gesundheit verbunden. Methoden zur Förderung der körperlichen Gesundheit sind gut bekannt: eine ausgewogene Ernährung, regelmäßige Bewegung sowie ausreichend Schlaf und Erholung. Bei der nicht minder wichtigen emotionalen Balance wird es schon etwas komplizierter. Stress abzubauen, die eigenen Grenzen zu kennen oder solche zum Schutz zu setzen sowie die Konzentration auf Positives und Sinnvolles wären Ansätze.
Der emotionale ist auch der Bereich, über den «Energie-Räuber» bevorzugt attackieren. Das sind zum Beispiel Dinge wie Überforderung, Perfektionismus oder mangelhafte Kommunikation. Social Media gehören ganz sicher auch dazu. Sie stehlen uns nicht nur Zeit, sondern sind höchst manipulativ und erhöhen laut einer aktuellen Studie das Risiko für psychische Probleme wie Angstzustände und Depressionen.
Geben wir negativen oder gar bösen Menschen keine Macht über uns. Das Dauerfeuer der letzten Jahre mit Krisen, Konflikten und Gefahren sollte man zwar kennen, darf sich aber davon nicht runterziehen lassen. Das Ziel derartiger konzertierter Aktionen ist vor allem, unsere innere Stabilität zu zerstören, denn dann sind wir leichter zu steuern. Aber Geduld: Selbst vermeintliche «Sonnenköniginnen» wie EU-Kommissionspräsidentin von der Leyen fallen, wenn die Zeit reif ist.
Es ist wichtig, dass wir unsere ganz eigenen Bedürfnisse und Werte erkennen. Unsere Energiequellen müssen wir identifizieren und aktiv nutzen. Dazu gehören soziale Kontakte genauso wie zum Beispiel Hobbys und Leidenschaften. Umgeben wir uns mit Sinnhaftigkeit und lassen wir uns nicht die Energie rauben!
Mein Wahlspruch ist schon lange: «Was die Menschen wirklich bewegt, ist die Kultur.» Jetzt im Frühjahr beginnt hier in Andalusien die Zeit der «Ferias», jener traditionellen Volksfeste, die vor Lebensfreude sprudeln. Konzentrieren wir uns auf die schönen Dinge und auf unsere eigenen Talente – soziale Verbundenheit wird helfen, unsere innere Kraft zu stärken und zu bewahren.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ f7d424b5:618c51e8
2025-05-18 18:03:25
@ f7d424b5:618c51e8
2025-05-18 18:03:25GAMERS, Join us for a vicless episode where we talk about AI for a change and how it has been impacting our lives. I promise it's video games related.
Stuff cited:
Obligatory:
- Listen to the new episode here!
- Discuss this episode on OUR NEW FORUM
- Get the RSS and Subscribe (this is a new feed URL, but the old one redirects here too!)
- Get a modern podcast app to use that RSS feed on at newpodcastapps.com
- Or listen to the show on the forum using the embedded Podverse player!
- Send your complaints here
Reminder that this is a Value4Value podcast so any support you can give us via a modern podcasting app is greatly appreciated and we will never bow to corporate sponsors!
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 4fa5d1c4:fd6c6e41
2025-05-16 13:15:47
@ 4fa5d1c4:fd6c6e41
2025-05-16 13:15:47Willkommen zur Mitmachplattform: KI-Kompetenzen für die religionsbezogene Bildung
Diese Plattform ist ein offenes, gemeinschaftliches Lernmodul für alle, die KI-Kompetenzen im Kontext der religionsbezogenen Bildung entdecken, vertiefen und weitergeben möchten.
Hier können Religionslehrende, Hochschulangehörige und ehrenamtlich Engagierte gemeinsam Inhalte entwickeln, teilen und weiterentwickeln.
Was ist das Ziel?
Wir schaffen eine offene Lernumgebung, in der Materialien zu KI-Kompetenzen für Schule, Hochschule und außerschulische Jugendarbeit kollaborativ entstehen.
Die Plattform richtet sich an Lehrkräfte, Fortbildner:innen und Ehrenamtliche, die KI-Themen in der religiösen Bildung verantwortungsvoll erschließbar machen wollen.
Unser Kompetenzmodell
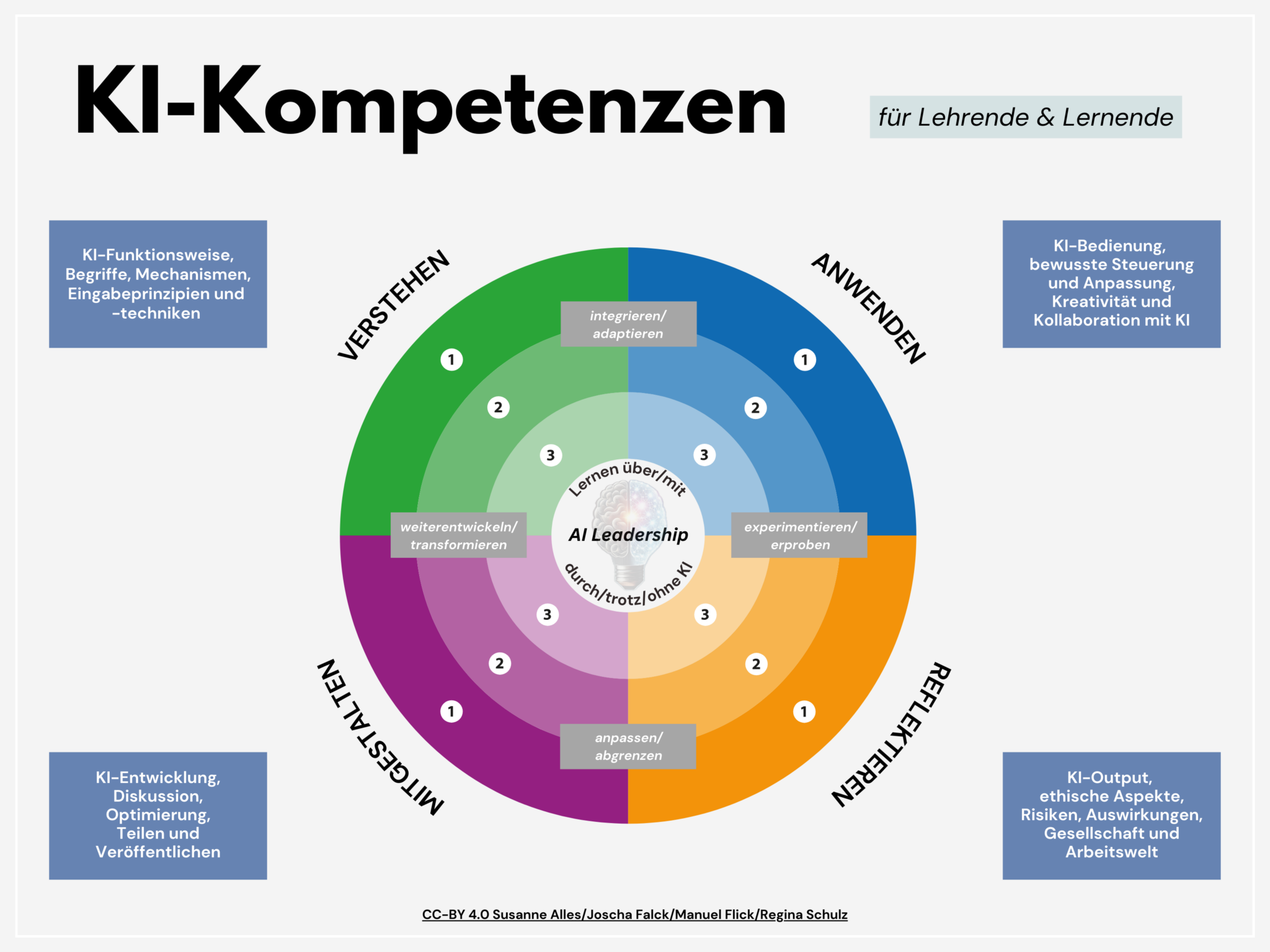
Im Zentrum steht ein Kreismodell mit vier Kompetenzbereichen, die auf drei Niveaustufen ausdifferenziert sind:
Verstehen, Anwenden, Reflektieren und Gestalten.
Diese Bereiche bauen aufeinander auf, beeinflussen sich gegenseitig und werden durch die zentrale Kompetenz AI Leadership verbunden.Im Zentrum steht ein Kreismodell mit vier Kompetenzbereichen, die auf drei Niveaustufen ausdifferenziert werden können:
Verstehen, Anwenden, Reflektieren und Gestalten.
Diese Bereiche bauen aufeinander auf, beeinflussen sich gegenseitig und werden durch die zentrale Kompetenz AI Leadership verbunden.| Kompetenzbereich | Beschreibung | |------------------|--------------| | 🟢 VERSTEHEN | Grundlagen und Mechanismen von KI | | 🔵 ANWENDEN | KI-Tools im Lernprozess nutzen | | 🟠 REFLEKTIEREN | Kritische Auseinandersetzung mit KI | | 🟣 GESTALTEN | Aktive Weiterentwicklung von KI-Systemen |
Jeder Lerninhalt ist einem Kompetenzbereich (und wenn möglich einer Niveaustufe) zugeordnet – farblich und inhaltlich klar erkennbar.
So funktioniert die Mitmachplattform
- Offene Inhalte: Alle Materialien werden als Markdown-Dateien über Nostr gepflegt.
- Mitmachen leicht gemacht: Egal wo auf Nostr du publizierst, mit den Hashtags #relilab und dem jeweiligen Kompetenzbereich als Schlagwort (also #verstehen, #anwenden, #gestalten, #reflektieren) finden wir diese Hashtagkombination und können die Webseite mit deiner Idee oder Weiterentwicklung ergänzen.
- Anleitungen: Eine eigene Seite erklärt Schritt für Schritt, wie du dich beteiligen kannst – ganz ohne Vorkenntnisse im Programmieren.
- Suchfunktion: Finde gezielt Inhalte nach Kompetenzbereich, Niveaustufe oder Schlagworten.
Für wen ist diese Plattform?
- Lehrkräfte an Schulen und Hochschulen in religionsbezogenen Fächern
- Ehrenamtliche und Multiplikator:innen in der kirchlichen Jugendarbeit
- Fort- und Weiterbildner:innen im Bereich KI und Religion
Mitmachen & Teilen
"Sharing is Caring":
Unser KI-Kompetenzmodell und alle Lernmaterialien stehen unter der offenen Lizenz [CC-BY 4.0].
Du darfst sie frei nutzen, anpassen und weitergeben – mit Nennung der Urheber:innen.
Starte jetzt!
Gemeinsam gestalten wir KI-Kompetenzen für eine reflektierte, verantwortungsvolle und kreative religiöse Bildung im KI-Zeitalter.
Kontakt & Feedback:
Für Fragen, Anregungen oder Feedback antworte einfach auf diese Nachricht oder komm' in den Matrix/Element-Raum #relilab-ki:rpi-virtuell zum Online-Austausch! -
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 4fa5d1c4:fd6c6e41
2025-05-16 11:42:12
@ 4fa5d1c4:fd6c6e41
2025-05-16 11:42:12Bibel-Selfies
Prompts
Eva, Schlange, Apfel und Adam

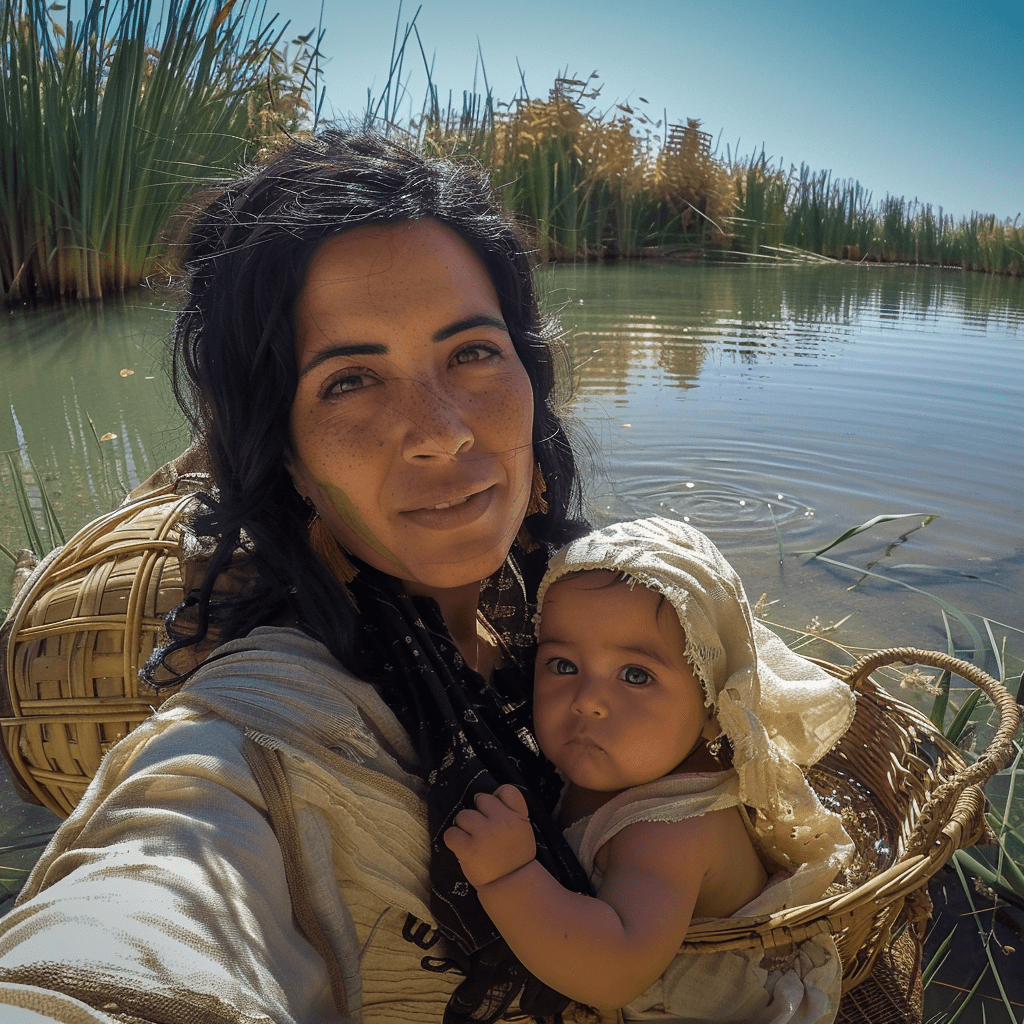
A selfie of a woman resembling eve in the time of old testament, blurred body, holding an apple, kneeling in front adam. he has a shocked expression with his mouth open and wide eyes, evoking a sense of both fear and surprise. The scene appears surreal, with a huge snake behind her. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with adam and eve, possibly at a place like garden eden. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudha --v 6.0Tochter des Pharao mit Mose
A selfie of the biblical figure moabite woman with her baby in front of an oasis. She is wearing traditional and has black hair. The background shows water from the desert oasis and grasses around it. In the Background a wicker basket on the water. The photo was taken in the style of a selfie shot with GoPro cameraSimon Petrus

A selfie of a man resembling Simon Petrus, wearing a white robe, surrounded by waves and thunderstorm. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with many waves behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus at the dead sea, possibly at a place like the sea. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Zachäus auf dem Baum
A selfie of a man resembling a roman in the time of jesus, wearing a glamorous robe, surrounded by the crown of a tree. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with many leaves behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus walking by, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Maria am Ostermorgen

A selfie of a woman resembling maria in the time of jesus, wearing a robe, kneeling in front of stone grave. she has a shocked expression with her mouth open and wide eyes, evoking a sense of both fear and surprise. The scene appears surreal, with the open glowing grave behind her. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus resurrection, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Der verlorene Sohn bei den Schweinen

A young ancient arabic man with short hair in the time of jesus, brown eyes, and a dirty face, covered in mud from working on his pig farm, takes an amateur selfie at dusk. He is surrounded by pig stables, with a barn visible in the background and pigs seen near the front. The photo captures a raw, authentic moment, as he gazes directly into the camera with an expression of excitement or wonder. The image has a realistic style, akin to Unsplash photography, and is meant to be posted on a primitive-themed social network. The resolution of the photo is high, style of selfie with gopro --v 6.0Vater und Sohn vereint
 A selfie of an Arab father in simple garments in the time of jesus, embracing and hugging a young man. The father's face, visible in the foreground, radiates joy and relief. Only the back of the son's head is visible, as he faces away from the camera, returning the embrace in tattered clothing. In the background, a large ancient house and other family members can be seen watching from a distance, blurred. The photo is taken with a wide-angle lens using a GoPro, enhancing the dramatic and overwhelming effect of the scene --v 6.0
A selfie of an Arab father in simple garments in the time of jesus, embracing and hugging a young man. The father's face, visible in the foreground, radiates joy and relief. Only the back of the son's head is visible, as he faces away from the camera, returning the embrace in tattered clothing. In the background, a large ancient house and other family members can be seen watching from a distance, blurred. The photo is taken with a wide-angle lens using a GoPro, enhancing the dramatic and overwhelming effect of the scene --v 6.0Bartimäus

A selfie of a man resembling blind bartimaeus in the time of jesus, black and brown and white bandages on his head over his eyes and face, wearing a robe, kneeling in front of a market place. he has a shocked expression with his mouth open and wide eyes still covered with black and brown and white bandages on his head, evoking a sense of both fear and surprise. The scene appears surreal, with many sand behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus healing the blind, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudha --v 6.0Daniel in der Löwengrube

A selfie of a man resembling Jesus, wearing a beige hoodie, surrounded by lions and cheetahs. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with many lions behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a lion's den, possibly at a place like the Grand Tabahar. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan ChaudharyDavid und Goliath

selfie of a the boy and shepherd david holding his slingshot resembling a fight with the giant goliath in the time of old testament, wearing a glamorous sligshot focusing on his giant opponent. David has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with a desert surrounding him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of the scene of David fighting with the giant goliath with his slingshot, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Simson im Philistertempel

A selfie of a man resembling simson in the time of old testament, wearing a glamorous beard and long hair, surrounded by thousands of ancient fighters. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with a temple surrounding him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus walking by, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Jona und der Wal

A selfie of a man resembling israeli jona in the time of old testament,`wearing a glamorous beard and long hair, inside the body of a whale. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with the ocean surrounding him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene in the bible. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary
Jakob und Isaak

A selfie of a young man resembling an ancient Arabic in clothes made of skins of goats and furs of the goats, looking overwhelmed and distressed as he betrays his father, who blesses him. The scene shows a dawn sky with hints of the sunrise, evoking a surreal and dramatic atmosphere. The scene is set in ancient Jerusalem, with stone buildings. in the background an old man with a gesture of blessing, rising his hands to the sky, The photo is taken with a wide-angle lens, blending surrealism with humor. The style is reminiscent of a GoPro selfie, capturing the intense moment with a sense of both fear and surprisePetrus und der Hahn

A selfie of a man resembling ancient young arabic man saint in traditional biblical attire, being eaten by a whale,. he has a shocked expression with his mouth pressed and wide eyes, evoking a sense of both fear and surprise. The scene appears surreal, with one rooster crowing out loud behind the man. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with peter and the rooster, possibly at a place in jerusalem . The style of the photo blends surrealism with humor, go pro selfie, morning dawn near sunrise settingJosef im Brunnen

A selfie of an ancient israelian man with a magical dreamcoat clothing in a deep well, looking at the camera from above, captured in the style of a go pro selfie stickElia und die Raben

A close-up selfie of a bearded man (Elijah) in biblical clothing, smiling gratefully. He is standing near a stream in a secluded, rocky area. Several black ravens are perched on his shoulders and arms, holding pieces of bread and meat in their beaks. The scene has a warm, golden light, symbolizing God's provision. Photorealistic style, high detail.Absalom im Baum

A selfie of a man resembling of a young man (Absalom) with long hair knotted arount the branches of a large oak tree.. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with all of his hairs knotted around the tree. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene of a robin hood movie in the forest . The style of the photo blends surrealism with humorRuth und Boas im Weizenfeld

A selfie of a young woman resembling Ruth, with a radiant smile and sun-kissed skin. She's standing in a golden wheat field at sunset, her arms filled with freshly gathered sheaves of wheat. Her hair is partially covered with a simple headscarf, with loose strands blowing in the wind. She has a look of joy and gratitude in her eyes. The scene appears idyllic, with wheat stalks seeming to embrace her. In the background, a distinguished older man (Boaz) can be seen watching from a distance, his expression a mix of curiosity and admiration. The photo is taken with a wide-angle lens, capturing the vastness of the field, the warmth of the setting sun, and Boaz in the distance. The setting is reminiscent of a biblical harvest scene. The style of the photo blends realism with a touch of romantic nostalgia."Bibel-Selfies" von Jörg Lohrer Lizenz: CC0 1.0
.
`
-
 @ 57d1a264:69f1fee1
2025-05-16 07:51:08
@ 57d1a264:69f1fee1
2025-05-16 07:51:08Payjoin allows the sender and receiver of an on-chain payment to collaborate and create a transaction that breaks on-chain heuristics, allowing a more private transaction with ambiguous payment amount and UTXO ownership. Additionally, it can also be used for UTXO consolidation (receiver saves future fees) and batching payments (receiver can make payment(s) of their own in the process of receiving one), also known as transaction cut-through. Other than improved privacy, the rest of the benefits are typically applicable to the receiver, not the sender.
BIP-78 was the original payjoin protocol that required the receiver to run a endpoint/server (always online) in order to mediate the payjoin process. Payjoin adoption has remained pretty low, something attributed to the server & perpetual online-ness requirement. This is the motivation for payjoin v2.
The purpose of the one-pager is to analyse the protocol, and highlight the UX issues or tradeoffs it entails, so that the payjoin user flows can be appropriately designed and the tradeoffs likewise communicated. A further document on UX solutions might be needed to identify solutions and opportunities
The following observations are generally limited to individual users transacting through their mobile devices:
While users naturally want better privacy and fee-savings, they also want to minimise friction and minimise (optimise) payment time. These are universal and more immediate needs since they deal with the user experience.
Added manual steps
TL;DR v2 payjoin eliminates server & simultaneous user-liveness requirements (increasing TAM, and opportunities to payjoin, as a result) by adding manual steps.
Usually, the extent of the receiver's involvement in the transaction process is limited to sharing their address with the sender. Once they share the address/URI, they can basically forget about it. In the target scenario for v2 payjoin, the receiver must come online again (except they have no way of knowing "when") to contribute input(s) and sign the PSBT. This can be unexpected, unintuitive and a bit of a hassle.
Usually (and even with payjoin v1), the sender crafts and broadcasts the transaction in one go; meaning the user's job is done within a few seconds/minutes. With payjoin v2, they must share the original-PSBT with the receiver, and then wait for them to do their part. Once the the receiver has done that, the sender must come online to review the transaction, sign it & broadcast.
In summary,
In payjoin v1, step 3 is automated and instant, so delay 2, 3 =~ 0. As the user experiences it, the process is completed in a single session, akin to a non-payjoin transaction.
With payjoin v2, Steps 2 & 3 in the above diagram are widely spread and noticeable. These manual steps are separated by uncertain delays (more on that below) when compared to a non-payjoin transaction.
Delays
We've established that both senders and receivers must take extra manual steps to execute a payoin transaction. With payjoin v2, this process gets split into multiple sessions, since the sender and receiver are not like to be online simultaneously.
Delay 2 & 3 (see diagram above) are uncertain in nature. Most users do not open their bitcoin wallets for days or weeks! The receiver must come online before the timeout hits in order for the payjoin process to work, otherwise time is just wasted with no benefit. UX or technical solutions are needed to minimise these delays.
Delays might be exacerbated if the setup is based on hardware wallet and/or uses multisig.
Notifications or background processes
There is one major problem when we say "the user must come online to..." but in reality the user has no way of knowing there is a payjoin PSBT waiting for them. After a PSBT is sent to the relay, the opposite user would only find out about it whenever they happen to come online. Notifications and background sync processes might be necessary to minimise delays. This is absolutely essential to avert timeouts in addition to saving valuable time. Another risk is phantom payjoin stuff after the timeout is expired if receiver-side does not know it has.
Fee Savings
The following observations might be generally applicable for both original and this v2 payjoin version. Fee-savings with payjoin is a tricky topic. Of course, overall a payjoin transaction is always cheaper than 2 separate transactions, since they get to share the overhead.
Additionally, without the receiver contributing to fees, the chosen fee rate of the PSBT (at the beginning) drops, and can lead to slower confirmation. From another perspective, a sender paying with payjoin pays higher fees for similar confirmation target. This has been observed in a production wallet years back. Given that total transaction time can extend to days, the fee environment itself might change, and all this must be considered when designing the UX.
Of course, there is nothing stopping the receiver from contributing to fees, but this idea is likely entirely novel to the bitcoin ecosystem (perhaps payments ecosystem in general) and the user base. Additionally, nominally it involves the user paying fees and tolerating delays just to receive bitcoin. Without explicit incentives/features that encourage receivers to participate, payjoining might seem like an unncessary hassle.
Overall, it seems that payjoin makes UX significant tradeoffs for important privacy (and potential fee-saving) benefits. This means that the UX might have to do significant heavy-lifting, to ensure that users are not surprised, confused or frustrated when they try to transact on-chain in a privacy-friendly feature. Good, timely communication, new features for consolidation & txn-cutthrough and guided user flows seem crucial to ensure payjoin adoption and for help make on-chain privacy a reality for users.
---------------
Original document available here. Reach out at
yashrajdca@proton.me,y_a_s_h_r_a_j.70on Signal, or on reach out in Bitcoin Design discord.https://stacker.news/items/981388
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 91bea5cd:1df4451c
2025-05-16 11:07:16
@ 91bea5cd:1df4451c
2025-05-16 11:07:16Instruções:
- Leia cada pergunta cuidadosamente.
- Escolha a opção (A, B, C ou D) que melhor descreve você na maioria das situações. Seja o mais honesto possível.
- Anote a letra correspondente à sua escolha para cada pergunta.
- No final, some quantas vezes você escolheu cada letra (A, B, C, D).
- Veja a seção de resultados para interpretar sua pontuação.
Teste de Temperamento
1. Em um evento social (festa, reunião), como você geralmente se comporta? A) Sou o centro das atenções, converso com todos, faço piadas e animo o ambiente. B) Tomo a iniciativa, organizo atividades ou discussões, e gosto de liderar conversas. C) Prefiro observar, conversar em grupos menores ou com pessoas que já conheço bem, e analiso o ambiente. D) Sou tranquilo, ouvinte, evito chamar atenção e me adapto ao ritmo do grupo.
2. Ao enfrentar um novo projeto ou tarefa desafiadora no trabalho ou estudo: A) Fico entusiasmado com a novidade, tenho muitas ideias iniciais, mas posso me distrair facilmente. B) Defino metas claras, crio um plano de ação rápido e foco em alcançar resultados eficientemente. C) Analiso todos os detalhes, planejo meticulosamente, prevejo possíveis problemas e busco a perfeição. D) Abordo com calma, trabalho de forma constante e organizada, e prefiro um ambiente sem pressão.
3. Como você geralmente reage a críticas? A) Tento levar na esportiva, talvez faça uma piada, mas posso me magoar momentaneamente e logo esqueço. B) Defendo meu ponto de vista vigorosamente, posso ficar irritado se sentir injustiça, mas foco em corrigir o problema. C) Levo muito a sério, analiso profundamente, posso me sentir magoado por um tempo e repenso minhas ações. D) Escuto com calma, considero a crítica objetivamente e tento não levar para o lado pessoal, buscando a paz.
4. Qual seu estilo de tomada de decisão? A) Sou impulsivo, decido rapidamente com base no entusiasmo do momento, às vezes me arrependo depois. B) Sou decidido e rápido, foco no objetivo final, às vezes sem considerar todos os detalhes ou sentimentos alheios. C) Sou ponderado, analiso todas as opções e consequências, demoro para decidir buscando a melhor escolha. D) Sou cauteloso, prefiro evitar decisões difíceis, busco consenso ou adio se possível.
5. Como você lida com rotina e repetição? A) Acho entediante rapidamente, preciso de variedade e novidade constante para me manter engajado. B) Tolero se for necessário para atingir um objetivo, mas prefiro desafios e mudanças que eu controlo. C) Aprecio a ordem e a previsibilidade, me sinto confortável com rotinas bem estabelecidas. D) Adapto-me bem à rotina, acho confortável e seguro, não gosto de mudanças bruscas.
6. Em uma discussão ou conflito: A) Tento aliviar a tensão com humor, expresso meus sentimentos abertamente, mas não guardo rancor. B) Sou direto e assertivo, defendo minha posição com firmeza, posso parecer confrontador. C) Evito confronto direto, mas fico remoendo o problema, analiso os argumentos e posso guardar ressentimento. D) Busco a conciliação, tento entender todos os lados, sou diplomático e evito o conflito a todo custo.
7. Como você expressa seus sentimentos (alegria, tristeza, raiva)? A) Expresso de forma aberta, intensa e visível, minhas emoções mudam rapidamente. B) Expresso de forma direta e forte, principalmente a raiva ou a determinação, controlo emoções "fracas". C) Tendo a internalizar, minhas emoções são profundas e duradouras, posso parecer reservado. D) Sou contido na expressão emocional, mantenho a calma externamente, mesmo que sinta algo internamente.
8. Qual seu nível de energia habitual? A) Alto, sou muito ativo, falante e entusiasmado, gosto de estar em movimento. B) Muito alto e direcionado, tenho muita energia para perseguir meus objetivos e liderar. C) Variável, posso ter picos de energia para projetos que me interessam, mas também preciso de tempo quieto para recarregar. D) Moderado e constante, sou calmo, tranquilo, prefiro atividades menos agitadas.
9. Como você organiza seu espaço de trabalho ou sua casa? A) Pode ser um pouco caótico e desorganizado, com muitas coisas interessantes espalhadas. B) Organizado de forma funcional para máxima eficiência, focado no essencial para as tarefas. C) Extremamente organizado, metódico, cada coisa em seu lugar, prezo pela ordem e estética. D) Confortável e prático, não necessariamente impecável, mas funcional e sem excessos.
10. O que mais te motiva? A) Reconhecimento social, diversão, novas experiências e interações. B) Poder, controle, desafios, alcançar metas ambiciosas e resultados concretos. C) Qualidade, significado, fazer as coisas da maneira certa, compreensão profunda. D) Paz, estabilidade, harmonia nos relacionamentos, evitar estresse e pressão.
11. Como você reage a imprevistos ou mudanças de plano? A) Adapto-me rapidamente, às vezes até gosto da novidade, embora possa atrapalhar meus planos iniciais. B) Fico irritado com a perda de controle, mas rapidamente busco uma solução alternativa para manter o objetivo. C) Sinto-me desconfortável e ansioso, preciso de tempo para reavaliar e replanejar cuidadosamente. D) Aceito com calma, sou flexível e me ajusto sem muito alarde, desde que não gere conflito.
12. Qual o seu maior medo (em termos gerais)? A) Ser rejeitado, ignorado ou ficar entediado. B) Perder o controle, parecer fraco ou incompetente. C) Cometer erros graves, ser inadequado ou imperfeito. D) Conflitos, pressão, tomar decisões erradas que afetem a estabilidade.
13. Como você costuma passar seu tempo livre? A) Socializando, saindo com amigos, buscando atividades novas e divertidas. B) Engajado em atividades produtivas, esportes competitivos, planejando próximos passos. C) Lendo, estudando, refletindo, dedicando-me a hobbies que exigem atenção e cuidado. D) Relaxando em casa, assistindo filmes, lendo tranquilamente, passando tempo com a família de forma calma.
14. Ao trabalhar em equipe: A) Sou o animador, trago ideias, conecto as pessoas, mas posso ter dificuldade em focar nos detalhes. B) Assumo a liderança naturalmente, delego tarefas, foco nos resultados e mantenho todos na linha. C) Sou o planejador e o crítico construtivo, atento aos detalhes, garanto a qualidade, mas posso ser muito exigente. D) Sou o pacificador e o colaborador, ajudo a manter a harmonia, realizo minhas tarefas de forma confiável.
15. Como você lida com prazos? A) Muitas vezes deixo para a última hora, trabalho melhor sob a pressão do prazo final, mas posso me atrapalhar. B) Gosto de terminar bem antes do prazo, vejo o prazo como um desafio a ser superado rapidamente. C) Planejo o tempo cuidadosamente para cumprir o prazo com qualidade, fico ansioso se o tempo fica curto. D) Trabalho em ritmo constante para cumprir o prazo sem estresse, não gosto de correria.
16. Qual destas frases mais te descreve? A) "A vida é uma festa!" B) "Se quer algo bem feito, faça você mesmo (ou mande fazer do seu jeito)." C) "Tudo tem um propósito e um lugar certo." D) "Devagar se vai ao longe."
17. Em relação a regras e procedimentos: A) Gosto de flexibilidade, às vezes acho as regras limitantes e tento contorná-las. B) Uso as regras a meu favor para atingir objetivos, mas não hesito em quebrá-las se necessário e se eu puder controlar as consequências. C) Sigo as regras rigorosamente, acredito que elas garantem ordem e qualidade. D) Respeito as regras para evitar problemas, prefiro seguir o fluxo estabelecido.
18. Como você reage quando alguém está emocionalmente abalado? A) Tento animar a pessoa, conto piadas, ofereço distração e companhia. B) Ofereço soluções práticas para o problema, foco em resolver a situação que causou o abalo. C) Escuto com empatia, ofereço apoio profundo e tento compreender a dor da pessoa. D) Mantenho a calma, ofereço um ouvido atento e um ombro amigo, sem me deixar abalar muito.
19. Que tipo de filme ou livro você prefere? A) Comédias, aventuras, romances leves, algo que me divirta e me mantenha entretido. B) Ação, suspense, biografias de líderes, estratégias, algo que me desafie ou inspire poder. C) Dramas profundos, documentários, mistérios complexos, ficção científica filosófica, algo que me faça pensar e sentir. D) Histórias tranquilas, dramas familiares, romances amenos, natureza, algo que me relaxe e traga conforto.
20. O que é mais importante para você em um relacionamento (amizade, amoroso)? A) Diversão, cumplicidade, comunicação aberta e espontaneidade. B) Lealdade, objetivos em comum, apoio mútuo nas ambições. C) Compreensão profunda, fidelidade, apoio emocional e intelectual. D) Harmonia, estabilidade, aceitação mútua e tranquilidade.
21. Se você ganhasse na loteria, qual seria sua primeira reação/ação? A) Faria uma grande festa, viajaria pelo mundo, compraria presentes para todos! B) Investiria estrategicamente, planejaria como multiplicar o dinheiro, garantiria o controle financeiro. C) Pesquisaria as melhores opções de investimento, faria um plano detalhado de longo prazo, doaria para causas significativas. D) Guardaria a maior parte em segurança, faria algumas melhorias práticas na vida, evitaria mudanças drásticas.
22. Como você se sente em relação a riscos? A) Gosto de arriscar se a recompensa parecer divertida ou excitante, sou otimista. B) Calculo os riscos e assumo-os se acreditar que a recompensa vale a pena e que posso controlar a situação. C) Evito riscos desnecessários, prefiro a segurança e a previsibilidade, analiso tudo antes de agir. D) Desgosto de riscos, prefiro caminhos seguros e comprovados, a estabilidade é mais importante.
23. Sua memória tende a focar mais em: A) Momentos divertidos, pessoas interessantes, experiências marcantes (embora possa esquecer detalhes). B) Sucessos, fracassos (para aprender), injustiças cometidas contra você, quem te ajudou ou atrapalhou. C) Detalhes precisos, conversas significativas, erros cometidos (por você ou outros), sentimentos profundos. D) Fatos objetivos, rotinas, informações práticas, geralmente de forma neutra.
24. Quando aprende algo novo, você prefere: A) Experimentar na prática imediatamente, aprender fazendo, mesmo que cometa erros. B) Entender o objetivo e a aplicação prática rapidamente, focar no essencial para usar o conhecimento. C) Estudar a fundo a teoria, entender todos os porquês, buscar fontes confiáveis e dominar o assunto. D) Aprender em um ritmo calmo, com instruções claras e passo a passo, sem pressão.
25. Se descreva em uma palavra (escolha a que mais se aproxima): A) Entusiasmado(a) B) Determinado(a) C) Criterioso(a) D) Pacífico(a)
26. Como você lida com o silêncio em uma conversa? A) Sinto-me desconfortável e tento preenchê-lo rapidamente com qualquer assunto. B) Uso o silêncio estrategicamente ou o interrompo para direcionar a conversa. C) Posso apreciar o silêncio para refletir, ou me sentir um pouco ansioso dependendo do contexto. D) Sinto-me confortável com o silêncio, não sinto necessidade de preenchê-lo.
27. O que te deixa mais frustrado(a)? A) Tédio, falta de reconhecimento, ser ignorado. B) Incompetência alheia, falta de controle, obstáculos aos seus planos. C) Desorganização, falta de qualidade, injustiça, superficialidade. D) Conflitos interpessoais, pressão excessiva, desordem emocional.
28. Qual a sua relação com o passado, presente e futuro? A) Foco no presente e nas oportunidades imediatas, otimista em relação ao futuro, esqueço o passado facilmente. B) Foco no futuro (metas) e no presente (ações para alcançá-las), aprendo com o passado mas não me prendo a ele. C) Reflito muito sobre o passado (aprendizados, erros), analiso o presente e planejo o futuro com cautela, às vezes com preocupação. D) Vivo o presente de forma tranquila, valorizo a estabilidade e a continuidade do passado, vejo o futuro com serenidade.
29. Se você tivesse que organizar um evento, qual seria seu papel principal? A) Relações públicas, divulgação, animação, garantir que todos se divirtam. B) Coordenação geral, definição de metas, delegação de tarefas, garantir que tudo aconteça conforme o planejado (por você). C) Planejamento detalhado, logística, controle de qualidade, garantir que nada dê errado. D) Suporte, resolução de problemas de forma calma, garantir um ambiente harmonioso.
30. Qual ambiente de trabalho te agrada mais? A) Dinâmico, social, com muita interação, flexibilidade e novidades. B) Competitivo, desafiador, focado em resultados, onde eu possa liderar ou ter autonomia. C) Estruturado, quieto, onde eu possa me concentrar, com padrões claros de qualidade e tempo para análise. D) Estável, cooperativo, sem pressão, com relacionamentos harmoniosos e tarefas previsíveis.
Calculando seus Resultados:
Agora, conte quantas vezes você escolheu cada letra:
- Total de A: ______
- Total de B: ______
- Total de C: ______
- Total de D: ______
A letra (ou as letras) com a maior pontuação indica(m) seu(s) temperamento(s) dominante(s).
Interpretação dos Resultados:
-
Se sua maior pontuação foi A: Temperamento SANGUÍNEO Dominante
- Características: Você é extrovertido, otimista, sociável, comunicativo, entusiasmado e adora novidades. Gosta de ser o centro das atenções, faz amigos facilmente e contagia os outros com sua energia. É criativo e espontâneo.
- Pontos Fortes: Carismático, inspirador, adaptável, bom em iniciar relacionamentos e projetos, perdoa facilmente.
- Desafios Potenciais: Pode ser indisciplinado, desorganizado, impulsivo, superficial, ter dificuldade em focar e terminar tarefas, e ser muito dependente de aprovação externa.
-
Se sua maior pontuação foi B: Temperamento COLÉRICO Dominante
- Características: Você é enérgico, decidido, líder nato, orientado para metas e resultados. É ambicioso, assertivo, direto e não tem medo de desafios ou confrontos. Gosta de estar no controle e é muito prático.
- Pontos Fortes: Determinado, eficiente, líder natural, bom em tomar decisões e resolver problemas, autoconfiante.
- Desafios Potenciais: Pode ser impaciente, dominador, teimoso, insensível aos sentimentos alheios, propenso à raiva e a "atropelar" os outros para atingir seus objetivos.
-
Se sua maior pontuação foi C: Temperamento MELANCÓLICO Dominante
- Características: Você é introvertido, analítico, sensível, perfeccionista e profundo. É leal, dedicado, aprecia a beleza e a ordem. Tende a ser pensativo, criterioso e busca significado em tudo. Leva as coisas a sério.
- Pontos Fortes: Detalhista, organizado, criativo (em profundidade), leal, empático, comprometido com a qualidade e a justiça.
- Desafios Potenciais: Pode ser pessimista, excessivamente crítico (consigo e com os outros), indeciso (pela análise excessiva), guardar ressentimentos, ser propenso à tristeza e ao isolamento.
-
Se sua maior pontuação foi D: Temperamento FLEUMÁTICO Dominante
- Características: Você é calmo, tranquilo, equilibrado e diplomático. É observador, paciente, confiável e fácil de conviver. Evita conflitos, busca harmonia e estabilidade. É um bom ouvinte e trabalha bem sob rotina.
- Pontos Fortes: Pacífico, estável, confiável, bom ouvinte, diplomático, eficiente em tarefas rotineiras, mantém a calma sob pressão.
- Desafios Potenciais: Pode ser indeciso, procrastinador, resistente a mudanças, parecer apático ou sem entusiasmo, ter dificuldade em se impor e expressar suas próprias necessidades.
Combinações de Temperamentos:
É muito comum ter pontuações altas em duas letras. Isso indica uma combinação de temperamentos. Por exemplo:
- Sanguíneo-Colérico: Extrovertido, enérgico, líder carismático, mas pode ser impulsivo e dominador.
- Sanguíneo-Fleumático: Sociável e agradável, mas pode ter dificuldade com disciplina e iniciativa.
- Colérico-Melancólico: Líder focado e detalhista, muito capaz, mas pode ser excessivamente crítico e exigente.
- Melancólico-Fleumático: Quieto, confiável, analítico, mas pode ser indeciso e resistente a riscos.
Importante: Este teste é uma ferramenta de autoconhecimento. Ninguém se encaixa perfeitamente em uma única caixa. Use os resultados para entender melhor suas tendências naturais, seus pontos fortes e as áreas onde você pode buscar equilíbrio e desenvolvimento.
-
 @ 57d1a264:69f1fee1
2025-05-16 05:38:28
@ 57d1a264:69f1fee1
2025-05-16 05:38:28LegoGPT generates a LEGO structure from a user-provided text prompt in an end-to-end manner. Notably, our generated LEGO structure is physically stable and buildable.
Lego is something most of us knows. This is a opportuity to ask where is our creativity going? From the art of crafting figures to building blocks following our need and desires to have a machine thinking and building following step-by-step instructions to achieve an isolated goal.
Is the creative act then in the question itself, not anymore in the crafting? Are we just delegating the solution of problems, the thinking of how to respond to questions, to machines? Would it be different if delegated to other people?
Source: https://avalovelace1.github.io/LegoGPT/
https://stacker.news/items/981336
-
 @ 57d1a264:69f1fee1
2025-05-14 09:48:43
@ 57d1a264:69f1fee1
2025-05-14 09:48:43Just another Ecash nutsnote design is a ew template for brrr.gandlaf.com cashu tocken printing machine and honoring Ecash ideator David Lee Chaum. Despite the turn the initial project took, we would not have Ecash today without his pioneering approach in cryptography and privacy-preserving technologies.
A simple KISS (Keep It Super Simple) Ecash nutsnote delivered as SVG, nothing fancy, designed in PenPot, an open source design tool, for slides, presentations, mockups and interactive prototypes.
Here Just another Nutsnote's current state, together with some snapshots along the process. Your feedback is more than welcome.
https://design.penpot.app/#/view?file-id=749aaa04-8836-81c6-8006-0b29916ec156&page-id=749aaa04-8836-81c6-8006-0b29916ec157§ion=interactions&index=0&share-id=addba4d5-28a4-8022-8006-2ecc4316ebb2
originally posted at https://stacker.news/items/979728
-
 @ cefb08d1:f419beff
2025-05-16 06:37:33
@ cefb08d1:f419beff
2025-05-16 06:37:33https://stacker.news/items/981350
-
 @ 866e0139:6a9334e5
2025-05-18 21:49:14
@ 866e0139:6a9334e5
2025-05-18 21:49:14Autor: Michael Meyen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
„Warum der Weltfrieden von Deutschland abhängt“ steht auf dem Cover. Sicher: Ein Verlag will verkaufen. Superlative machen sich da immer gut. Der Weltfrieden und Deutschland. „Wie das“, wird mancher fragen, über den Atlantik schauen, nach Kiew oder gar nach Moskau und nach Peking, und die 24 Euro ausgeben. Ich kann nur sagen: Das ist gut investiert, wenn man verstehen will, was uns die Nachrichtensprecher und ihre Kritiker im Moment alles um die Ohren hauen. Ich durfte die Texte von Hauke Ritz schon lesen und ein Vorwort schreiben, in dem es nicht nur um Krieg und Frieden geht, sondern auch um die Frage, warum sich manche, die einst „links“ zu stehen glaubten, inzwischen mit einigen Konservativen besser vertragen als mit den alten Genossen – nicht nur bei der Gretchenfrage auf dem Cover. Nun aber zu meinem Vorwort.
1. Der Leser
Hauke Ritz hat meinen Blick auf die Welt verändert. In diesem Satz stecken zwei Menschen. Ich fange mit dem Leser an, weil jeder Text auf einen Erfahrungsberg trifft, gewachsen durch all das, was Herkunft, soziale Position und Energievorrat ermöglichen. Ob ein Autor dort auf Resonanz stößt, kann er nicht beeinflussen. Also zunächst etwas zu mir. Ich bin auf der Insel Rügen aufgewachsen – in einer kommunistischen Familie und mit Karl Marx. Das Sein bestimmt das Bewusstsein. In der Schule haben wir Kinder uns über ein anderes Marx-Zitat amüsiert, das in einem der Räume groß an der Wand stand. „Die Philosophen haben die Welt nur verschieden interpretiert, es kömmt drauf an, sie zu verändern.“ Kömmt. Dieser Marx. Was der sich traut.
Das Schulhaus ist nach 1990 schnell abgerissen worden. Bauland mit Meerblick, fünf Minuten bis zum Strand. Marx stand nun zwar kaum noch in der Zeitung, Eltern, Freunde und Bekannte waren sich aber trotzdem sicher, dass er Recht hat. Das Sein bestimmt das Bewusstsein. Hier die Ostdeutschen, auf Jahre gebunden im Kampf um Arbeitsplatz und Qualifikationsnachweise, Rente und Grundstück, und dort Glücksritter aus dem Westen, die sich das Dorf kaufen und nach ihrem Bilde formen. Das Kapital live in Aktion gewissermaßen.
Ich selbst bin damals eher durch Zufall an der Universität gelandet und habe dort eine Spielart der Medienforschung kennengelernt, die in den USA erfunden worden war, um den Zweiten Weltkrieg nicht nur auf dem Schlachtfeld zu gewinnen, sondern auch in den Köpfen. Diese akademische Disziplin konnte und wollte nach ihrer Ankunft in der alten Bundesrepublik nichts mit Marx am Hut haben. Zum einen war da dieser neue Freund auf der anderen Atlantikseite, moralisch sauber und damit ein Garant gegen den Vorwurf, mitgemacht zu haben und vielleicht sogar Goebbels und sein Postulat von den Medien als Führungsmittel immer noch in sich zu tragen. Je lauter dieser Vorwurf wurde, desto stärker zog es deutsche Propagandaforscher, die sich zur Tarnung Kommunikations- oder Publizistikwissenschaftler nannten, in die USA.
Zum anderen verbannte der Radikalenerlass jeden Hauch von Marxismus aus dem universitären Leben. Selbst Postmarxisten wie Adorno und Horkheimer mit ihrer Frankfurter Schule, Karl Mannheim oder Pierre Bourdieu, auf die ich bei der Suche nach einer neuen intellektuellen Heimat fast zwangsläufig gestoßen bin, spielten in den Lehrveranstaltungen kaum eine Rolle und damit auch nicht in Dissertationen, Habilitationen, Fachzeitschriften. Peer Review wird schnell zur Farce, wenn jeder Gutachter weiß, dass bestimmte Texte nur von mir und meinen Schülern zitiert werden. Ich habe dann versucht, die Kollegen mit Foucault zu überraschen, aber auch das hat nicht lange funktioniert.
Zu Hauke Ritz ist es von da immer noch weit. Ich habe eine Lungenembolie gebraucht (2013), zwei Auftritte bei KenFM (2018) und die Attacken, die auf diese beiden Interviews zielten sowie auf meinen Blog Medienrealität, gestartet 2017 und zeitgleich mit großen Abendveranstaltungen aus der virtuellen Welt in die Uni-Wirklichkeit geholt, um bereit zu sein für diesen Denker. Corona nicht zu vergessen. Ich erinnere mich noch genau an diesen Abend. Narrative Nummer 16 im August 2020. Hauke Ritz zu Gast bei Robert Cibis, Filmemacher und Kopf von Ovalmedia. Da saß jemand, der mühelos durch die Geschichte spazierte und es dabei schaffte, geistige und materielle Welt zusammenzubringen. Meine Götter Marx, Bourdieu und Foucault, wenn man so will, angereichert mit mehr als einem Schuss Religionswissen, um die jemand wie ich, als Atheist erzogen und immer noch aufgeregt, wenn er vor einer Kirche steht, eher einen Bogen macht. Dazu all das, was ich in tapsigen Schritten auf dem Gebiet der historischen Forschung zu erkunden versucht hatte – nur in weit längeren Zeiträumen und mit der Vogelperspektive, die jede gute Analyse braucht. Und ich kannte diesen Mann nicht. Ein Armutszeugnis nach mehr als einem Vierteljahrhundert in Bewusstseinsindustrie und Ideologieproduktion.
2. Der Autor
Und damit endlich zu diesem Autor, der meinen Blick auf die Welt verändert hat. Hauke Ritz, Jahrgang 1975, ist ein Kind der alten deutschen Universität. Er hat an der FU Berlin studiert, als man dort noch Professoren treffen konnte, denen Eigenständigkeit wichtiger war als Leistungspunkte, Deadlines und politische Korrektheit. Seine Dissertation wurzelt in diesem ganz anderen akademischen Milieu. Ein dickes Buch, in dem es um Geschichtsphilosophie geht und um die Frage, welchen Reim sich die Deutschen vom Ersten Weltkrieg bis zum Fall der Berliner Mauer auf den Siegeszug von Wissenschaft und Technik gemacht haben. Das klingt sehr akademisch, wird aber schnell politisch, wenn man die Aufsätze liest, die Hauke Ritz ab den späten Nullerjahren auf diesem Fundament aufgebaut hat und die hier nun in einer Art Best-of in die Öffentlichkeit zurückgeholt werden aus dem Halbdunkel von Publikationsorten, deren Reputation inzwischen zum Teil gezielt zerstört worden ist, und die so hoffentlich ein großes und neues Publikum erreichen. In den Texten, die auf dieses Vorwort folgen, geht es um den tiefen Staat und den neuen kalten Krieg, um Geopolitik und Informationskriege und dabei immer wieder auch um die geistige Krise der westlichen Welt sowie um den fehlenden Realitätssinn deutscher Außenpolitik.
Bevor ich darauf zurückkomme, muss ich die Doppelbiografie abrunden, mit der ich eingestiegen bin. Im Februar 2022, wir erinnern uns auch mit Hilfe des Interviews, das Paul Schreyer mit ihm führte, war Hauke Ritz gerade in Moskau, als Universitätslehrer auf Zeit mit einem DAAD-Stipendium. Im November 2024, als ich diese Zeilen schreibe, ist er wieder einmal in China, mit familiären Verbindungen. Das heißt auch: Hauke Ritz hat mehr gesehen, als einem in den Kongresshotels der US-dominierten Forschergemeinschaften je geboten werden kann. Und er muss weder um Zitationen buhlen noch um irgendwelche Fördertöpfe und damit auch nicht um das Wohlwollen von Kollegen.
Ein Lehrstuhl oder eine Dozentenstelle, hat er mir im Frühsommer 2021 auf Usedom erzählt, wo wir uns das erste Mal gesehen haben, so eine ganz normale akademische Karriere sei für ihn nicht in Frage gekommen. Der Publikationsdruck, die Denkschablonen. Lieber ökonomisch unsicher, aber dafür geistig frei. Ich habe mir diesen Satz gemerkt, weil er einen Beamten wie mich zwingt, seinen Lebensentwurf auf den Prüfstand zu stellen. Bin ich beim Lesen, Forschen, Schreiben so unabhängig, wie ich mir das stets einzureden versuche? Wo sind die Grenzen, die eine Universität und all die Zwänge setzen, die mit dem Kampf um Reputation verbunden sind? Und was ist mit dem Lockmittel Pension, das jeder verspielt, der das Schiff vor der Zeit verlassen will?
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Hauke Ritz, das zeigen die zehn Aufsätze, die in diesem Buch versammelt sind, hat alles richtig gemacht. Hier präsentiert sich ein Autor, der „von links“ aufgebrochen ist und sich immer noch so sieht (so beschreibt er das dort, wo es um die aktuelle Theorieschwäche des einst gerade hier so dominanten Lagers geht), aber trotzdem keine Angst hat, für ein Wertesystem zu werben, das eher konservativ wirkt. Herkunft und Familie zum Beispiel. Verankerung und Zugehörigkeit, sowohl geografisch als auch intellektuell. Mehr noch: Wenn ich Hauke Ritz richtig verstanden habe, dann braucht es ein Amalgam aus den Restbeständen der »alten« Linken und dem christlich geprägten Teil des konservativen Lagers, um eine Entwicklung aufzuhalten und vielleicht sogar umzukehren, die in seinen Texten das Etikett »Postmoderne« trägt. Grenzen sprengen, Identitäten schleifen, Traditionen vergessen. Umwertung aller Werte. Transgender und Trans- oder sogar Posthumanismus. Wer all das nicht mag, findet in diesem Buch ein Reiseziel. Gerechtigkeit und Utopie, Wahrheitssuche, der Glaube an die Schöpferkraft des Menschen und die geistige Regulierung politischer Macht – verwurzelt in der Topografie Europas, die Konkurrenz erzwang, und vor allem im Christentum, weitergetragen in weltlichen Religionen wie dem Kommunismus, und so attraktiv, dass Hauke Ritz von Universalismus sprechen kann, von der Fähigkeit dieser Kultur, ein Leitstern für die Welt zu sein.
Ich habe die Texte im Frühling 2022 gelesen, allesamt in einem Rutsch, um mich auf das Gespräch vorzubereiten, das ich mit Hauke Ritz dann im Juni für die Plattform Apolut geführt habe, den Nachfolger von KenFM. Ich weiß, dass das ein Privileg ist. Lesen, worauf man Lust hat, und dafür auch noch bezahlt werden. Ich weiß auch, dass ich ohne die Vorgeschichte, ohne Corona und all das, was mich und dieses Land dorthin geführt hat, niemals das Glück hätte empfinden können, das mit der Entdeckung eines Autors wie Hauke Ritz verbunden ist. Ohne all das wäre ich wahrscheinlich weiter zu irgendwelchen hochwichtigen Tagungen in die USA geflogen und hätte mich mit Aufsätzen für Fachzeitschriften gequält, die für einen winzigen Kreis von Eingeweihten gemacht und selbst von diesem Kreis allenfalls registriert, aber nicht studiert werden.
Lange Gespräche mit Köpfen wie Hauke Ritz hatten bei Ovalmedia oder Apolut in den Coronajahren sechsstellige Zuschauerzahlen. Ein großes Publikum, wenn man die Komplexität und die Originalität mitdenkt, die jeder Leser gleich genießen kann. Man findet diese Videos noch, allerdings nicht beim De-facto-Monopolisten YouTube, der Zensur sei Dank. Im Bermudadreieck zwischen Berlin, Brüssel und dem Silicon Valley verschwindet alles, was die hegemonialen Narrative herausfordert und das Potenzial hat, Menschenmassen erst zu erreichen und dann zu bewegen. Ich habe Hauke Ritz deshalb schon im Studio und am Abend nach unserem Dreh ermutigt und wahrscheinlich sogar ein wenig gedrängt, aus seinen Aufsätzen ein Buch zu machen. Das war auch ein wenig egoistisch gedacht: Ich wollte mein Aha-Erlebnis mit anderen teilen und so Gleichgesinnte heranziehen. Der Mensch ist ein Herdentier und mag es nicht, allein und isoliert zu sein.
3. Ein neuer Blick auf Macht
Drei Jahre später gibt es nicht nur die Aufsatzsammlung, die Sie gerade in den Händen halten, sondern auch ein Buch, das ich als „großen Wurf“ beschrieben habe – als Werk eines Autors, der die Wirklichkeit nicht ignoriert (Geografie, Reichtum und die Geschichte mit ihren ganz realen Folgen), sich aber trotzdem von der Vorstellung löst, dass der Mensch in all seinem Streben und Irren nicht mehr sei als ein Produkt der Umstände. Hauke Ritz dreht den Spieß um: Die Geschichte bewegt nicht uns, sondern wir bewegen sie. Was passiert, das passiert auch und vielleicht sogar in erster Linie, weil wir ganz bestimmte Vorstellungen von der Vergangenheit und unserem Platz in dieser Welt verinnerlicht haben. Von diesem Axiom ist es nur ein klitzekleiner Schritt zur Machtpolitik: Wenn es stimmt, dass das historische Bewusstsein mindestens genauso wichtig ist wie Atomsprengköpfe, Soldaten oder Gasfelder, dann können sich die Geheimdienste nicht auf Überwachung und Kontrolle beschränken. Dann müssen sie in die Ideenproduktion eingreifen. Und wir? Wir müssen die Geistesgeschichte neu schreiben, Politik anders sehen und zuallererst begreifen, dass der Mensch das Sein verändern kann, wenn er denn versteht, wer und was seinen Blick bisher gelenkt hat. Ich bin deshalb besonders froh, dass es auch das Herz der Serie „Die Logik des neuen kalten Krieges“ in dieses Buch geschafft hat, ursprünglich 2016 bei RT-Deutsch erschienen. Diese Stücke sind exemplarisch für das Denken von Hauke Ritz. Der Neoliberalismus, um das nur an einem Beispiel zu illustrieren, wird dort von ihm nicht ökonomisch interpretiert, „sondern als ein Kulturmodell“, das zu verstehen hilft, wie es zu der Ehe von Kapitalismus und „neuer Linker“ kommen konnte und damit sowohl zu jener „aggressiven Dominanz des Westens“, die auch den Westend-Verlag umtreibt und so diese Publikation ermöglicht, als auch zur „Vernachlässigung der sozialen Frage“.
Hauke Ritz holt die geistige Dimension von Herrschen und Beherrschtwerden ins Scheinwerferlicht und fragt nach der „Macht des Konzepts“. Diese Macht, sagt Hauke Ritz nicht nur in seinem Aufsatz über die „kulturelle Dimension des Kalten Krieges“, hat 1989/90 den Zweikampf der Systeme entschieden. Nicht die Ökonomie, nicht das Wohlstandsgefälle, nicht das Wettrüsten. Ein Riesenreich wie die Sowjetunion, kaum verschuldet, autark durch Rohstoffe und in der Lage, jeden Feind abzuschrecken, habe weder seine Satellitenstaaten aufgeben müssen noch sich selbst – wenn da nicht der Sog gewesen wäre, der von der Rockmusik ausging, von Jeans und Hollywood, von bunten Schaufenstern und von einem Märchen, das das andere Lager als Hort von Mitbestimmung, Pressefreiheit und ganz privatem Glück gepriesen hat. Als selbst der erste Mann im Kreml all das für bare Münze nahm und Glasnost ausrief (das, was der Westen für seinen Journalismus bis heute behauptet, aber schon damals nicht einlösen konnte und wollte), sei es um den Gegenentwurf geschehen gewesen. Die Berliner Mauer habe der Psychologie nicht standhalten können.
Fast noch wichtiger: All das war kein Zufall, sondern Resultat strategischer und vor allem geheimdienstlicher Arbeit. Hauke Ritz kann sich hier unter anderem auf Francis Stonor Saunders und Michael Hochgeschwender stützen und so herausarbeiten, wie die CIA über den Kongress für kulturelle Freiheit in den 1950ern und 1960ern Schriftsteller und Journalisten finanzierte, Musiker und Maler, Zeitschriften, Galerien, Filme – und damit Personal, Denkmuster, Symbole. Die „neue“ Linke, „nicht-kommunistisch“, also nicht mehr an der System- und Eigentumsfrage interessiert, diese „neue“ Linke ist, das lernen wir bei Hauke Ritz, genauso ein Produkt von Ideenmanagement wie das positive US-Bild vieler Westeuropäer oder eine neue französische Philosophie um Michel Foucault, Claude Lévi-Strauss oder Bernard-Henri Lévy, die Marx und Hegel abwählte, stattdessen auf Nietzsche setzte und so ein Fundament schuf für das „Projekt einer Umwertung aller Werte“.
Natürlich kann man fragen: Was hat all das mit uns zu tun? Mit dem Krieg in der Ukraine, mit der Zukunft Europas oder gar mit der These auf dem Buchcover, dass nichts weniger als der „Weltfrieden“ ausgerechnet von uns, von Deutschland abhängt? Warum sollen wir uns mit Kämpfen in irgendwelchen Studierstübchen beschäftigen, die höchstens zwei Handvoll Gelehrte verstehen? Hauke Ritz sagt: Wer die Welt beherrschen will, muss den Code der europäischen Kultur umschreiben. Wie weit dieses „Projekt“ schon gediehen ist, sieht jeder, der die Augen öffnet. In der Lesart von Hauke Ritz ist Europa Opfer einer „postmodernen Fehlinterpretation seiner eigenen Kultur“, importiert aus den USA und nur abzuwehren mit Hilfe von Russland, das zwar zu Europa gehöre, sich vom Westen des Kontinents aber unterscheide und deshalb einen Gegenentwurf liefern könne. Stichworte sind hier Orthodoxie und Sozialismus sowie eine Vergangenheit als Imperium, ohne die, so sieht das Hauke Ritz, neben diplomatischen Erfahrungen die „politischen Energien“ fehlen, die nötig sind, um Souveränität auch da zu bewahren, wo die „Macht des Konzepts“ beginnt. China und der Iran ja, Indien und Lateinamerika nein.
Keine Angst, ich schreibe hier kein zweites Buch. Diese Appetithäppchen sollen Lust machen auf einen Autor, der die Hektik der Gegenwart hinter sich lässt und aus den Tiefen der Geschichte eine Interpretation anbietet, die die hegemoniale Ideologie in ein ganz neues Licht rückt und sie so als „Rechtfertigungslehre“ enttarnt (Werner Hofmann) oder als „Machtinterpretation der Wirklichkeit“ (Václav Havel), die sich zwangsläufig „ritualisiert“ und „von der Wirklichkeit emanzipiert“, um als „Alibi“ für alle funktionieren zu können, die mit der Macht marschieren. Ich weiß nicht mehr, wie ich das Marx-Zitat mit dem komischen Wort „kömmt“ als kleiner Junge gedeutet habe. Ich wusste wenig von Philosophie und gar nichts von der Welt. Hauke Ritz blickt nicht nur in Abgründe, die ich vorher allenfalls aus dem Augenwinkel gesehen hatte, sondern bietet zugleich eine Lösung an. Als Gleichung und in seinen Worten formuliert: „klassische Arbeiterbewegung“ plus „christlich orientierte Wertkonservative“ ist gleich Hoffnung und Neustart. Und nun Vorhang auf für einen Philosophen, der nicht nur Deutschland einen Weg weist in Richtung Veränderung und Frieden.
Michael Meyen ist Medienforscher, Ausbilder und Journalist. Seit 2002 ist er Universitätsprofessor an der LMU München. https://www.freie-medienakademie.de/
Der Link zum Buch von Hauke Ritz
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 57d1a264:69f1fee1
2025-05-14 06:48:45
@ 57d1a264:69f1fee1
2025-05-14 06:48:45Has the architect Greg Chasen considered it when rebuilding the house just one year before the catastrophe? Apparently not! Another of his projects was featured on the Value of Architecture as properties with design integrity.
This is a super interesting subject. The historic character, livability, and modern disaster-resistance is a triangle where you often have to pick just one or two, which leads to some tough decisions that have major impacts on families and communities. Like one of the things he mentions is that the architect completely eliminated plants from the property. That's great for fire resistance, but not so great for other things if the entire town decides to go the same route (which he does bring up later in the video). I don't think there's any objectively right answer, but definitely lots of good (and important) discussion points to be had.
https://www.youtube.com/watch?v=cbl_1qfsFXk
originally posted at https://stacker.news/items/979653
-
 @ efe5d120:1fc51981
2025-05-15 12:53:31
@ efe5d120:1fc51981
2025-05-15 12:53:31It’s not big government programs or powerful institutions that make a society strong. It’s something much simpler: everyday people trading and working together.
Think about the local hardware store owner. He helps his neighbors, gives people jobs, and provides useful tools. But when the government taxes him too much to fund its programs, it takes away money he could have used to hire someone or visit his family. That hurts both him and the people around him.
This happens all over. Small business owners, tradesmen, inventors and entrepreneurs are the ones who really build up a society. They create value by trading things people want, and both sides benefit. Free trade gives people more choices and helps them live better lives.
But from a young age, we’re told to obey authority without question. We’re taught that without rulers, there would be chaos. But what if that’s not true?
Look around the world: even when governments try to control trade, people still find ways to work together and exchange goods. It’s natural. People want to cooperate and help each other—especially when they’re free to do so.
Here’s the hard truth: if someone can take your money, control your property, and punish you without your agreement, isn’t that a kind of control—or even servitude?
True prosperity doesn’t come from the top down. It comes from people freely working together—farmers, builders, cooks, coders—offering their skills to others who need them.
When trade is free, people do well. When it’s blocked by too many rules or taxes, everyone loses—especially the ones who need help the most.
The answer isn’t more laws or more control. It’s more freedom. Next time someone says we need more government to fix things, ask yourself: wouldn’t free people solve those problems better on their own?
Real civilization isn’t about being ruled. It’s about choosing to work together, trade fairly, and respect each other’s rights. That’s not chaos—that’s freedom.
-
 @ df478568:2a951e67
2025-05-18 21:29:52
@ df478568:2a951e67
2025-05-18 21:29:52Mene sells investment grade, 24 kt gold jewelry. 24kt gold is 100% atomic number 79, AU, gold like a nugget. More pure than Ivory soap. Best of all, you can buy it the greatest money ever made. By the way, this really is not investment advice. I am bearish on the gold/bitcoin trade anyway. I'm old enough to remember [when a whole coin first became worth more than an ounce of gold.
nostr:nevent1qqsrssrzndmlv6vatcsg5ahzz9hy9k7026x4fq2ntwh3zfaw6hdtj0cjmjyn9.
Unfortunately, I didn't have an ounce of gold back then. I only had a few grams I didn't sell for bitcoin and like eight fiat bucks.
Gold is about gifts for me. I don't have any gold myself, except for an 18 kt gold necklace my grandmother gave me when I was seven. I'm never selling it I would have a lot more bitcoin if I sold that necklace when bitcoin was $200, but I keep it for sentimental reasons. It's not about the money, it's about the utility of gold.
Reduce Your Non-Strategic Future Trash Reserve
I don't like spending sats on stuff you expect to throw away within 5 years or less. l'll buy a pair of shoes very now and then, but it doesn't make sense to go on a shopping spree at The Dollar Tree, where nothing is a dollar, nor built to last. Expect everything you buy at The Dollar Tree to be buried in a landfill within a few years.
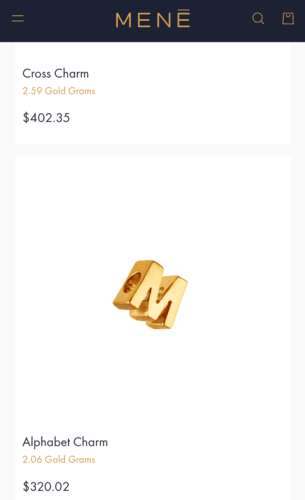
Consider this your non-strategic future trash reserve. Every 1,000 sats you don't spend is a thousand sats stacked. Put those sats into your Strategic Bitcoin Reserve instead of your non-strategic future trash reserve.
*“He is so rich, he has no room to shit.”
– Marcus Aurelius, Meditations*
People Don't Throw Gold Away
I still have that gold necklace even though it no longer fits my neck. If you buy someone a smart watch, you can bet your last sat it will help fill a landfill within 5 years or less. This is not financial advice. If you give the gift of a 24 kt. gold bracelet, you know it won't be thrown away. It might get stolen or sold, but nobody in their right mind is throwing gold away like a sock with holes in it.
That's why I like buying gold as a gift. Besides, my wife and daughter both like gold jewelery. Go figure. I have given them sats before. They prefer the gold. Well, my wife doesn't want to spend the sats anymore, but she did. In the old 144 block days, she She used to joke, "My husband never shuts up about bitcoin. It's money we can't spend. That's not the case anymore. Block by block, bitcoin is accepted more and more places. Menē accepts bitcoin for gold Jewelry.
I don't know if Menē stacks sats, but they do use the lightning network. I doubt they keep the sats. They use BitPay, the company BTCpayServer set out to destroy. I still use bitcoin over the lightning network to stack sats because, like BTCPins says…
Gold Is Stack-able
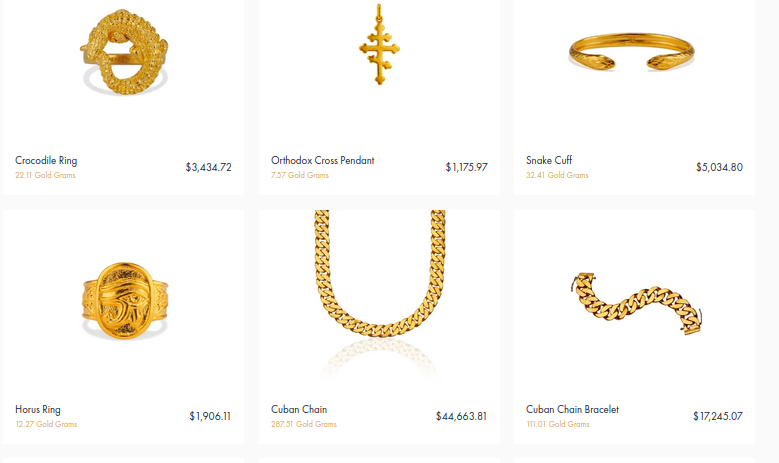
I'm not saying to spend your whole stack on a Cuban Link. You can start small. Buy a charm. It will come with a free leather strap, but just so you know, it's a trap. My wife said she loves the charm, but needs a charm bracelet to go with it because she's not wearing a strap. Good, now I know what to get her for Christmas. You could save sats for something nice though and many of the pieces are stack-able. Maybe you can't afford a whole ounce today. Buy a few grams and add to it as the blocks go by and the charms presumably become cheaper. Gold is the bigger asset right now and it has gone up quite a bit recently, but bitcoin is hovering just below the Gold/bitcoin all time high. i can't predict the future, but I want to re-iterate, just because they market this as investment jewelry, I am not saying this is investment advice. This is about giving the gift of bitcoin 1.0.
There's a metric ton of different charms that can be added to a bracelet or necklace. This makes gold a gift that keeps on giving. Buy a bracelet for her birthday this year and you can buy her a charm next year. They say bitcoin is digital gold. What better way to begin teaching people digital gold than by using analog gold? Again, I don't expect gold to be the biggest asset in the world for long. This is about showing your loved ones that bitcoin is better than gold.
You can spend sats at Menē. They will send you 100% pure gold. They charge spot for the gold and add a 25% fee for their labor. They will send your gift to the destination of your choice. You can even set the delivery date if you order in advance. Each piece is hand crafted and made to order like Burger King, but built to last and no seed oil. Best of all, they have 44,441 reviews as of block 897,304.
Each piece also comes with a letter of authenticity. It shows how many grams of 100% gold it's made of. It's not as good as a UTXO, but they say the jewelry is as good as gold. If you want to give bitcoin away, buy one of my birthday cards, but if you want to buy something your loved ones won't throw away, buy Menē. They accept bitcoin for tariff-free gold jewelry, hand-crafted in the United States of America. They accept bitcoin, but you know what they don't accept? Gold because bitcoin is better than gold for selling gold on the Internet.
Menē Is Great!
I give Menē two emoji 5-of-5 orange hearts. They make great gifts worthy of people who stand to inherit generational wealth.
🧡🧡🧡🧡🧡
npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
-
 @ cefb08d1:f419beff
2025-05-15 06:48:32
@ cefb08d1:f419beff
2025-05-15 06:48:32originally posted at https://stacker.news/items/980537
-
 @ 3f770d65:7a745b24
2025-05-14 18:26:17
@ 3f770d65:7a745b24
2025-05-14 18:26:17🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qyx8wumn8ghj7cnjvghxjmcpz4mhxue69uhk2er9dchxummnw3ezumrpdejqqgxchnavlnv8t5vky5dsa87ddye0jc8z9eza8ekvfryf3yt649mytvhadgpe , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 57d1a264:69f1fee1
2025-05-14 06:12:19
@ 57d1a264:69f1fee1
2025-05-14 06:12:19We asked members of the design community to choose an artifact that embodies craft—something that speaks to their understanding of what it means to make with intention. Here’s what they shared.
A vintage puzzle box, a perfectly tuned guitar, an AI-powered poetry camera. A daiquiri mixed with precision. A spreadsheet that still haunts muscle memory. Each artifact tells a story: not just about the thing itself, but about the choices of the creator behind it. What to refine, what to leave raw. When to push forward, when to let go. Whether built to last for generations or designed to delight in a fleeting moment, the common thread is that great craft doesn’t happen by accident. It’s made.
On the application of craft
Even the most experienced makers can benefit from building structure and intention into their practice. From sharpening your storytelling to designing quality products, these pieces offer practical ways to uplevel your craft.
Read more at https://www.figma.com/blog/craft-artifacts/
originally posted at https://stacker.news/items/979644
-
 @ a5ee4475:2ca75401
2025-05-18 21:09:53
@ a5ee4475:2ca75401
2025-05-18 21:09:53clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 📱 (on development) ⏳
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
- Keychat - Signal based [🤖🍎 on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] [source] 🤖🍎
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ cefb08d1:f419beff
2025-05-14 06:28:50
@ cefb08d1:f419beff
2025-05-14 06:28:50originally posted at https://stacker.news/items/979646
-
 @ 57d1a264:69f1fee1
2025-05-14 05:56:15
@ 57d1a264:69f1fee1
2025-05-14 05:56:15Shanghai: Bus Stops Here
A new crowd-sourced transit platform allows riders to propose, vote on, and activate new bus lines in as little as three days.
From early-morning school drop-offs to seniors booking rides to the hospital, from suburban commuters seeking a faster link to the metro to families visiting ancestral graves, Shanghai is rolling out a new kind of public bus — one that’s designed by commuters, and launched only when enough riders request it.
Branded “DZ” for dingzhi, or “customized,” the system invites residents to submit proposed routes through a city-run platform. Others with similar travel needs can opt in or vote, and if demand meets the threshold — typically 15 to 20 passengers per trip — the route goes live.
More than 220 DZ routes have already launched across all 16 city districts. Through an online platform opened May 8, users enter start and end points, preferred times, and trip frequency. If approved, routes can begin running in as little as three days.
Continue reading at https://www.sixthtone.com/news/1017072
originally posted at https://stacker.news/items/979637
-
 @ 8d34bd24:414be32b
2025-05-18 20:43:56
@ 8d34bd24:414be32b
2025-05-18 20:43:56We are all supposed to share Jesus and His word with those around us. We are called to:
but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence (1 Peter 3:15)
We should daily pray to God, read the Bible, and share Jesus with others. Some Christians will choose to go into full-time service to God. They will be pastors or missionaries. They will work for churches, Christian schools, and other Christian ministries. Of course, not everyone will make serving Jesus a career. That doesn’t mean the non-career Christians have no job to do. We are all to be a light to this world.
There is one ministry, though, that I’d argue is most important: sharing the gospel with and discipling our children.
These words, which I am commanding you today, shall be on your heart. You shall teach them diligently to your sons and shall talk of them when you sit in your house and when you walk by the way and when you lie down and when you rise up. (Deuteronomy 6:6-7)
This passage may have been written in the Old Testament, but I’d argue that it is even more true now that we have the truth of Jesus Christ, “the way, the truth, and the life.” If the Jews were called to diligently teach their kids the law, how much more should Christians diligently teach their kids the wonderous works and words of Jesus?
Train up a child in the way he should go, Even when he is old he will not depart from it. (Proverbs 22:6)
We should be so excited about what Jesus has done for us that it flows out of us in our daily lives. We should have a strong desire to learn God’s word and to share it with others, especially our children. We should share our excitement about Jesus with our kids. We should share our gratefulness for all Jesus has done for us. We should share our excitement about doing God’s work. Our children should see our faith in all we do and say.
Taking our kids to church Sunday morning and to Sunday school or youth group once a week is not going to teach our kids the importance of faith in Jesus. Praying openly at meals, at bedtime, when we hear about someone in need, and when a difficult situation happens teaches our kids to rely on Jesus. Reading our Bibles in front of our kids and doing daily devotions (at whatever time works for you, but we do evenings) teaches them the importance of the Scriptures. Acting according to a Biblical worldview and taking the time to explain to our kids the answers to the hard questions when the culture contradicts the Bible. This may mean taking the time to research answers to your kids’ questions because you don’t know the answer. Being patient with our kids, and even apologizing to them when we fail, teaches them to be humble and to repent. As the old saying goes, “morals are caught more than taught.” Also faith in Jesus is caught more than taught.
We need to live Godly lives that are different than the culture, remembering that our children are always watching, even when they are quite young and can’t articulate what they are learning.
We need to actively teach God’s word. This may be summarizing principles when they are young, but as soon as possible, this should include reading God’s word to our kids. (My daily reading is usually in an NASB Bible, but it is difficult for a young child to understand with its long, complex sentences, so I recommend something like the NLT Bible for children.)
“Now this is the commandment, the statutes and the judgments which the Lord your God has commanded me to teach you, that you might do them in the land where you are going over to possess it, so that you and your son and your grandson might fear the Lord your God, to keep all His statutes and His commandments which I command you, all the days of your life, and that your days may be prolonged. (Deuteronomy 6:1-2) {emphasis mine}
We want to share all of our knowledge of God and the Bible with our kids, grandkids, and great grandkids. We want to disciple our kids into strong faith in God and knowledge of the Bible, so they are capable of training their kids and their grandkids. We want to multiply faith in our families.
It is definitely good to have scheduled, intentional times of training our kids about the Bible. This could be part of homeschooling (which I strongly recommend). This could be family devotions, but we want teaching our kids about God to be just a natural part of life.
You shall teach them to your sons, talking of them when you sit in your house and when you walk along the road and when you lie down and when you rise up. (Deuteronomy 11:19)
Talking about what God has done in our lives, what we have learned about in our personal Bible study, and how the Bible relates to things we see in life should all naturally flow out of our interactions together. Talk about what the Bible says about a subject you hear on the news. Talk about what the Bible says about what is happening in a movie you watch. Talk about what the Bible says about the decisions you and your kids are having to make. Talk about what the Bible says about your kids’ relationship with each other and their friends and parents. God should be a normal part of everything in life.
We also want to make sure our actions don’t drive our kids away from God.
Fathers, do not provoke your children to anger, but bring them up in the discipline and instruction of the Lord. (Ephesians 6:4)
The Bible does not make light of our need to train our kids in faith.
Discipline your son while there is hope, And do not desire his death. (Proverbs 19:18)
This is so important that failure to train up our kids in faith is considered desiring our kid’s death.
God finds this training so critical, He also addresses it from the kid’s point of view and commands them to listen to their parent’s teaching.
My son, give attention to my words;\ Incline your ear to my sayings.\ Do not let them depart from your sight;\ Keep them in the midst of your heart.\ For they are life to those who find them\ And health to all their body.\ Watch over your heart with all diligence,\ For from it flow the springs of life. (Proverbs 4:20-23)
In Proverbs 31, the Bible gives the best explanation of a Godly woman and mother.
She opens her mouth in wisdom,\ And the teaching of kindness is on her tongue.\ She looks well to the ways of her household,\ And does not eat the bread of idleness.\ *Her children rise up and bless her*;\ Her husband also, and he praises her, saying:\ “Many daughters have done nobly,\ But you excel them all.” (Proverbs 31:26-29)
A Mom should continually “open her mouth in wisdom,” and teach kindly. A mother who fulfills this commandment faithfully is promised that “Her children rise up and bless her.” Being loved and appreciated by our kids is a wonderful blessing, but even greater is knowing that we will see our children with us in heaven.
May God guide you and encourage you as you teach, train, and discipline your kids to know their God, Creator, and Savior.
Trust Jesus.
-
 @ 7460b7fd:4fc4e74b
2025-05-18 11:02:09
@ 7460b7fd:4fc4e74b
2025-05-18 11:02:09比特币持有者在 iPhone 上的安全使用注意事项
引言:iPhone 与安卓的对比
当涉及移动设备安全,比特币持有者面临着在 iPhone 和安卓设备之间的选择。从安全硬件来看,安卓阵营中确有一些型号配备了类似于 Apple Secure Enclave 的硬件安全模块,例如 Google Pixel 手机内置的 Titan M/M2 安全芯片,用于保障启动流程和存储敏感数据us.norton.com;三星的旗舰机型则集成了 Samsung Knox 多层安全平台,经过多国政府机构认证,可在硬件层面保护设备及其中数据us.norton.com。这些安全措施大大提升了设备抵御恶意攻击和数据泄露的能力。然而,需要注意的是:具备此类高级安全特性的安卓机型在市场上相对少见,并非安卓阵营的普遍标准us.norton.com。安卓生态高度碎片化,不同厂商的安全实践差异悬殊;除了少数注重安全的厂商(如 Google、Samsung)外,许多设备缺乏统一的安全保障水平us.norton.com。尤其在二手市场上,安卓设备型号繁杂且来源不一,一些旧款或改装机型可能缺少最新的安全芯片或更新,使安全性难以得到保证。
相比之下,Apple iPhone 全系列自带硬件级的安全隔区(Secure Enclave),统一的闭源系统和严格的应用审核使其安全措施在所有设备上保持一致us.norton.com。同时,iPhone 引入的 Face ID(三维结构光人脸识别)在生物识别安全性上具有独特优势。Apple官方数据显示,Face ID 被他人解锁的概率只有 百万分之一,远低于指纹识别的五万分之一。这源于Face ID利用红外点阵投射捕捉面部3D结构,难以被照片或面具所破解,大幅减少了伪造生物特征解锁的风险。此外,相较许多安卓手机仍依赖的二维人脸识别或电容/光学指纹,Face ID 在抗攻击能力上更胜一筹——例如普通指纹残留可能被提取复制,而二维人脸解锁曾被照片轻易骗过,但Face ID的深度感应技术有效避免了这些漏洞。
综上所述,在移动设备安全领域,iPhone 为比特币等高价值敏感资产的持有者提供了更为稳健和统一的安全基础。尽管某些高端安卓手机具有可圈可点的安全功能,但鉴于这类机型凤毛麟角、安卓设备更新和管控的不统一,以及生物识别方案的差异,我们强烈建议将 iPhone 作为比特币手持设备的唯一选择。从硬件加密到生物识别,iPhone 的封闭生态和领先技术能为数字资产提供更可靠的防护,而安卓设备在这一场景下则存在诸多先天不足。
小结: 安卓阵营虽有Pixel Titan芯片、Samsung Knox等亮点,但安全机型数量有限且良莠不齐;iPhone凭借统一的安全架构和先进的Face ID,在保护敏感数据方面更胜一筹。为确保比特币等资产安全,选择安全可靠的iPhone 是明智之举。
iPhone 安全配置指南
选择了 iPhone 作为比特币存取和通讯设备后,仍需进行细致的安全设置,以最大化利用其安全潜力。以下是针对比特币持有者的 iPhone 安全配置要点:
-
禁用 Face ID/Touch ID 生物解锁,改用强PIN码: 建议关闭面容ID解锁功能,改用6位以上的数字PIN码(或更复杂的字母数字密码)作为解锁方式。在紧急情况下,生物识别容易被他人强制利用(例如他人将手机对准机主面部强行解锁),而记忆型的PIN码只有持有人知晓,更难以被胁迫获取。此外,法律上某些地区对强制提供生物特征和提供密码有所区别,这也使得使用PIN码在极端情况下更有保障。
-
启用自动锁定(1分钟) 将设备设为闲置1分钟后自动锁定屏幕。从安全角度出发,锁定等待时间越短越好。1分钟的设置可确保即使暂时离开或疏忽,设备也会很快上锁,防范他人乘虚而入。养成随手锁屏的习惯固然重要,但有了短自动锁定时间作为双重保障,安全性更上一层楼。
-
开启输错10次自动抹除: 在“设置 > 面容ID/触控ID与密码”中启用“连续输错10次密码抹掉数据”功能。一旦有人反复尝试猜测密码,该功能会在第十次错误尝试后自动抹除手机数据。很多用户担心该设置存在风险,但事实上 误触发的可能性极低。sspai.comsspai.com实际测试表明,iPhone在多次输错密码时会触发累进的延迟惩罚机制:第五次错误需要等待1分钟,第六次错误等待5分钟,第7-8次各等待15分钟,第9次等待1小时sspai.comsspai.com。要连续进行十次独立的错误尝试至少需要约96分钟,在现实中“熊孩子”乱按连续清空数据几乎不可能发生sspai.com。相反,该功能对抗暴力破解极为有效——正如2015年圣贝纳迪诺恐怖袭击案中,嫌犯所用的iPhone就启用了十次错误清除,使FBI也无法轻易尝试破解en.wikipedia.org。总之,此项设置能将设备落入他人之手时的数据泄露风险降至最低。
-
利用应用级 Face ID 控制(iOS 18+):升级至iOS 18或更新版本,充分利用其新增的应用锁定功能。长按主屏某个应用图标,可以找到“需要Face ID”选项,将该应用加锁theverge.com。被加锁的应用每次打开都需要通过Face ID身份验证(即使手机已解锁)。建议对 聊天通讯、密码管理、交易所App 等敏感应用启用此功能。例如,将微信、Signal、邮件客户端等设置为打开需Face ID验证,以防范他人在您手机解锁的短暂间隙内获取其中内容。应用级Face ID锁定为设备提供了第二道防线:即使手机本身已解锁,敏感应用和数据仍受到保护。
-
建议购买第二台 iPhone 或 iPad 作为“备用解锁入口”: 利用 Apple 的“信任链”机制,为同一 Apple ID 配置多台受信任设备(如两台 iPhone 或 iPhone+iPad)。这样即使主设备丢失或被抹除,备用设备依然可以访问并恢复 iCloud 端到端加密数据。其安全本质类似于“1-of-N 多签”,即任一设备均可独立解锁所有云数据,但无需多设备联合协商,恢复更灵活。注意:这与比特币的m-of-n多签不同,Apple的信任链是单设备多入口,安全性和便利性权衡需根据个人需求评估。官方说明参见:Apple平台安全白皮书(Keychain与信任链)
-
建议购买 YubiKey 等硬件安全密钥作为 Apple ID 验证要素: 由于信任链机制下新设备加入时,身份验证成为潜在攻击点(如钓鱼、社工、短信劫持),推荐为 Apple ID 配置 YubiKey 或兼容 FIDO2/U2F 的硬件安全密钥。启用后,只有插入并触发硬件密钥的情况下,才能完成新设备授权、敏感操作或账户恢复,有效阻止网络钓鱼和大部分远程攻击。该方法可显著提升账户安全,降低因凭证泄漏或验证被劫持导致的信任链攻破风险。Apple 官方说明:为 Apple ID 添加安全密钥
通过上述配置,iPhone 将处于一个平衡了便利性和安全性的状态:日常解锁采用PIN码确保意外情况下设备不被强制解锁,短自动锁和十次清除严防暴力破解,而应用级加锁进一步保障重要数据不外泄。
小结: 按照以上指南对iPhone进行安全配置,可以大幅提升设备在实际使用中的抗攻击能力。生物识别解锁的取舍、自动锁定和清除机制、以及iOS 18引入的应用加锁功能相结合,全方位地巩固了手机作为比特币手持设备的安全基石。
关于自动抹除的常见质疑回应
启用“输错10次自动抹除”功能后,不少用户会提出疑虑,主要集中在两个方面:其一,担心儿童误操作或本人一时疏忽导致设备数据被抹掉;其二,担心万一手机数据被抹除,设备本身价值受损。针对这些质疑,我们进行如下回应:
-
“熊孩子乱按怎么办?” 前文已提及,iPhone设计了渐进延时机制,使得连续十次错误输入并非易事sspai.comsspai.com。孩子无意识地反复点击相同数字,系统只视为一次错误sspai.com;而多次不同错误则会触发越来越长的锁定时间,很难真的连续试满十次sspai.com。实践中,要触发十次错误清除需要近两个小时且每次输入都不同,这种情景极不现实sspai.com。因此,只要平时看护好设备,误抹除几乎无需担心。相反,如果没有该功能,一旦设备遗失或被不法分子获取,后果将不堪设想——对方可以在足够时间和专业工具协助下尝试无限次解锁,从而获取您手机中的一切秘密。
-
“数据没了岂不可惜?” 我们强调,比特币持有者手机中存储的敏感信息价值远超设备本身。手机里可能有助记词、私钥线索、交易记录截图,甚至包含您社交账户中关于资产的对话。在攻击者眼中,这些数据的价值胜过一部手机。与其担心设备被误清除,不如担心设备落入他人之手数据遭泄露的风险。况且,对于重要数据您应当早有备份(下文将讨论启用iCloud云备份的问题)。即使真发生误清除,有备份在手也能恢复;但若数据被不法分子窃取,一旦造成资产损失将无法挽回。因此,从风险权衡来看,“宁可误删,不可被盗”——自动抹除是最后一道保障,在极端情况下保护您的数字资产不被侵害。
总而言之,这一功能的利远大于弊。儿童误触可以通过良好监护和系统延时设计来防范,而一旦启用,您将获得巨大的安心:手机若遭试图破解,可以自毁以保全数据安全。这正是比特币持有者应有的安全理念:舍弃设备保安全,数据和资产永远优先于硬件。随着良好备份策略的配合(例如iCloud加密备份),启用自动抹除几乎没有后顾之忧。
小结: 针对自动抹除功能的疑虑更多是误解。iPhone的机制使得误触发几率极低,而其提供的数据安全保障却是无可替代的。比特币等敏感资产持有者应放下顾虑,优先保护数据安全——哪怕代价是设备被清除,也胜过数据落入他人之手。
iCloud 备份的争议与建议
在确保本地设备安全的同时,妥善备份数据同样关键。对于比特币持有者而言,启用 iCloud 云备份可以提供额外的一层安心:万一设备遗失、损坏或被抹除后,仍有机会恢复重要信息。然而,围绕iCloud备份的安全性一直存在争议,我们在此详细分析并给出建议:
首先强烈建议在启用iCloud备份的同时,务必开启「高级数据保护」(Advanced Data Protection, ADP)。默认情况下,iCloud云备份的数据加密密钥由Apple掌管,这意味着苹果公司在法律要求下能够解密并提供您的备份数据support.apple.comsupport.apple.com。而开启高级数据保护后,备份所涉及的大部分数据将采用端对端加密,只有您的受信任设备掌握解锁密钥support.apple.com。据苹果官方说明,在ADP模式下,即便苹果公司也无法读取您的备份内容support.apple.com。因此,高级数据保护能够将使用云备份可能带来的隐私泄露风险降至最低(前提是您妥善保管好自己的账户和恢复密钥)。
启用云备份常见的疑虑是:“会不会把我的钱包私钥也备份上去,万一云被攻破岂不危险?” 实际上,多数主流比特币/加密钱包软件不会将核心密钥(如助记词或扩展公钥xpub)存储在云备份中。很多钱包在设计时就要求用户自行备份助记词,而不会把这些高度敏感的数据写入应用沙盒,可被iCloud备份抓取。同样地,一些钱包应用甚至提醒用户关闭iCloud备份以防助记词泄露support.wallet.coinex.com。换言之,开启iCloud备份并不会将您的私钥上传(除非个别钱包特别设置了云同步,但大多数非托管钱包都没有这么做)。当然,为审慎起见,您可以查阅所用钱包的文档或设置,确认其是否有备份敏感信息到云的选项,并据此做出取舍。
与此同时,我们更加关心的是其他应用的数据完整备份。对于比特币持有者来说,聊天记录、笔记文档和工作应用的数据往往同样敏感且重要。例如,常用通讯软件(微信、Telegram、Signal 等)中的聊天可能涉及交易细节或人脉网络;办公应用如钉钉、飞书则包含财务往来或业务资料。这些应用的数据都会包含在iCloud整机备份中并被完整保存,一旦手机丢失或损坏,可以通过云备份原样恢复。support.apple.com值得一提的是,在高级数据保护开启且不泄漏密钥的前提下,这些备份数据即使存储在苹果服务器上也是安全的,第三方无法解读其中内容。
进一步的好处是:利用备份进行调查取证。假设最坏情况发生——您的手机被抹除或遗失,但是事先有一份最新的iCloud备份。在紧急需要时,您可以在一台新的iPhone上恢复这份备份。在恢复完成后,切断新设备的网络连接(拔掉SIM卡或不连Wi-Fi)。由于备份恢复会还原您的应用登录状态和本地数据,新设备在离线情况下将维持原手机当时的登录环境。您可以打开聊天应用、邮件、照片等查看内容,就像原手机一样。离线操作确保应用不会因为检测到新设备而要求重新登录,也避免了云端数据被远程清除的可能。这对于事后取证、提供线索给执法部门或自我调查都极为有利。比如,若涉及盗窃诈骗案件,这部离线恢复的手机里保留的聊天记录、交易凭证可以作为关键证据。而一旦联网,这些应用可能出于安全考虑登出账户或拉取最新状态,反而不利于保留原始证据。因此,有意识地保存一份完整云备份,并在需要时以离线方式恢复,是一种非常巧妙的应对策略。
小结: 尽管人们对云备份心存疑虑,但通过启用高级数据保护,iCloud备份既能提供数据恢复便利,又充分保障了隐私安全。大多数加密钱包不会上传私钥等核心数据,而聊天、办公等应用的数据则可完整份以备不时之需。在平衡安全与可用性的前提下,开启iCloud备份(搭配ADP加密)是明智之举——它让您在设备意外损坏或丢失时依然有据可查、有据可证。
高级数据保护与密码学机制分析
最后,我们从更宏观的视角,结合真实案例和技术原理,深入探讨苹果设备与云服务的安全性,以及高级数据保护(ADP)所依赖的密码学机制。这部分将涵盖苹果在多个国家遭遇的解锁争议、ADP 的运作及其与实体安全密钥的配合、以及关于苹果是否存在解密后门的分析。
苹果与执法部门的解锁事件
过去数年间,多起高调事件凸显了设备加密与执法取证之间的矛盾。美国国会山骚乱事件(2021年1月6日)中,执法部门缴获了大量嫌疑人的手机。据报道,不少嫌犯使用的是iPhone,调查人员能够从苹果获取其中的数据 但途径主要是通过 iCloud 云备份 而非直接破解设备thedailybeast.com。由于当时高级数据保护尚未推出或未启用,苹果依然持有那些嫌疑人iCloud账户的备份密钥,因此在收到合法的执法请求后,苹果向FBI提供了嫌疑人的iCloud备份内容,其中包括视频、照片和聊天记录等关键证据thedailybeast.com。这些数据帮助当局重构了案件过程,也反映出如果用户没有使用端到端加密备份,云端数据在法律压力下并非牢不可破。
相反,在更早的**圣贝纳迪诺恐怖袭击案(2015)**中,FBI面对一部启用了强加密的嫌犯iPhone却陷入僵局。那是一个运行iOS 9的 iPhone 5C,开启了PIN码锁和10次输错清除功能en.wikipedia.org。由于该设备上的本地数据经过设备加密且苹果并不持有密钥,FBI无法提取其中信息,遂求助苹果公司要求破解。但苹果以维护所有用户安全为由拒绝编写后门固件来绕过安全限制,引发了一场著名的法律拉锯en.wikipedia.orgen.wikipedia.org。最终执法部门辗转通过第三方工具解锁了手机,但苹果的立场十分明确:即便面对恐怖主义案件,也不会为单次事件在系统中留下后门。这一事件凸显出现代iPhone设备本地加密之强大——在没有用户密码的情况下,即使连厂商都无能为力,除非另辟蹊径寻求系统或硬件漏洞。
iCloud 在中国与英国的访问争议
在不同国家,苹果围绕用户数据加密与政府监管的博弈也在上演。中国方面,自2018年以来苹果将中国大陆 iCloud 服务交由“云上贵州”公司运营,数据存储和加密密钥均留在境内zh.amnesty.org。依据中国《网络安全法》,云服务运营者有义务为执法和国家安全机关提供“技术支持和协助”zh.amnesty.org。这意味着若中国警方出于刑侦需要向云上贵州调取某用户的 iCloud 数据,该公司必须配合提供,几乎没有拒绝的空间zh.amnesty.org。更重要的是,苹果把中国用户的 iCloud 加密密钥也存放在中国,一旦收到合法命令要求解密数据,苹果和云上贵州只能遵从zh.amnesty.org。换言之,在标准数据保护模式下,中国当局有途径通过法律手段获取本地存储的iCloud明文数据。这引发了人们对隐私的担忧:如果没有端到端加密,中国的用户数据可能在政府要求下被查看。然而如果用户开启高级数据保护,使得苹果也无法解读备份内容,那么即便在中国,此举从技术上为用户争取到了更高的私密性(前提是中国地区允许开启ADP——截至目前,苹果并未在中国禁用该功能,国区用户依然可以自行启用高级数据保护support.apple.comsupport.apple.com)。
再看英国的情况。英国政府近年以打击犯罪和恐怖主义为由,不断向科技公司施压要求提供加密数据的后门访问权。2023年底,英国援引《调查权力法》(IPA)秘密向苹果发出“技术能力通知”(TCN),要求苹果在全球范围内为英国安全部门提供对加密iCloud内容的解锁途径cnbeta.com.tw。这实际上等同于要求苹果破坏其端到端加密体系,留出一个只有政府能用的后门。苹果对此断然拒绝,并做出强硬回应:宁愿撤除在英服务,也不会妥协安全底线cnbeta.com.tw。结果是,苹果选择在英国境内停止提供高级数据保护功能给新用户。已有启用ADP的英国用户被通知需在宽限期内手动将其关闭,否则将无法继续使用iCloud备份cnbeta.com.tw。苹果在声明中表示对此深感失望,但为了遵守当地法律别无他法cnbeta.com.tw。下面这张截图显示了英国用户在系统中看到的提示信息,明确告知ADP服务不再可用

苹果针对英国地区做出的ADP功能调整通知。英国政府要求能够解密用户数据,迫使苹果撤回了对英国用户的新端到端加密备份支持cnbeta.com.twcnbeta.com.tw。苹果声明强调只有用户本人才能解读其加密数据,并重申不会在产品中留下执法后门cnbeta.com.tw。
这一英国内外的罕见举措表明,各国政府正日益重视加密带来的执法障碍,而苹果则在平衡用户隐私和法律要求之间走钢丝。尽管英国的情况迫使苹果让步(取消当地ADP),但苹果并未真的为政府打造解密后门,而是通过限制功能来表明态度——这与其长期立场一致:绝不在加密产品中留后门,即使承受业务上的损失cnbeta.com.tw。
高级数据保护与安全密钥
高级数据保护(ADP) 是苹果于 iOS 16.2 引入的一项可选功能,其核心是在用户选择开启后,将包括设备备份在内的大部分 iCloud 数据升级为端到端加密存储support.apple.comsupport.apple.com。开启ADP有两个前提:账户已启用双重认证,以及设置了账户恢复联系人或恢复密钥,以防用户遗失访问权限support.apple.comsupport.apple.com。在ADP模式下,Apple不再持有绝大部分云数据的解锁密钥,这些密钥只存在于用户的受信任设备中support.apple.com。这意味着,即便苹果公司收到政府索取数据的要求或其服务器遭黑客攻击,没有密钥的加密数据对任何第三方都是无意义的乱码。正如苹果声明所言:“只有拥有数据的用户才能解密,Apple 无法访问端对端加密的数据”cnbeta.com.tw。可以说,ADP将用户云数据的主导权完全交还给用户自己,从而彻底消除了苹果方面潜在的数据泄露点。
为了进一步增强账户安全,苹果在_iOS 16.3_开始支持绑定实体安全密钥(如 YubiKey)作为 Apple ID 的额外两步验证方式sspai.com。过去Apple ID登录主要依赖密码+发送到受信设备的验证码,但假如用户Apple ID密码泄露,攻击者可能利用社会工程获取验证码。而引入实体安全密钥后,用户可以要求任何新的登录尝试都必须提供物理密钥认证才能完成。这相当于给 Apple ID 上了一把“硬件锁”。对于比特币持有者而言,这一步非常值得配置:即使黑客骗取了您的苹果账号密码,没有您的YubiKey或同类FIDO2安全密钥,他仍无法登录您的iCloud或停用您的ADP。安全密钥本身具有防钓鱼特性,它不会把可被重用的机密泄露给假网站,再加上密钥私藏于硬件内部不可导出,使得账户保护达到新的高度sspai.comsspai.com。简而言之,**“ADP + 硬件安全密钥”**的组合为用户云数据打造了双重护城河:前者确保云上数据加密不被窥探,后者确保账户本身不被劫持利用。
需要注意的是,启用ADP后如果遗失所有设备且忘记密码,苹果无法帮您找回数据support.apple.com。这就像您把保险箱钥匙只握在自己手里而不交给任何人保管,其安全性空前提高,但也意味着责任完全在您。因此请务必牢记Apple ID密码,保管好恢复密钥或紧急联系人。一旦平衡好便利与安全,这套机制将为您的数字资产提供堪比硬件钱包的云端保障。
后门密钥与私钥不可拆分性
现代加密体系的设计使得用户私钥与设备环境密不可分。在苹果的生态中,每台设备都拥有由硬件生成的唯一加密根密钥。例如,安全隔区(Secure Enclave)内嵌入了设备唯一标识符UID作为根密钥,UID由安全硬件随机生成并烧录至芯片中help.apple.com。这个UID既不与任何其他设备标识相关,也无法被设备外的任何人(包括苹果官方)获取help.apple.com。同时,用户的解锁密码与该UID进行数学“交织”(entangle),共同派生出加密密钥help.apple.com。换言之,设备硬件密钥和用户密码共同决定了数据加密密钥,没有这两者就无法还原密钥。这体现了用户私钥对设备及用户身份的强绑定——苹果没有第三方密钥可以绕过这一绑定关系help.apple.comhelp.apple.com。
从密码学角度来看,如果苹果试图在上述体系中插入一个额外的“后门密钥”,将面临巨大的技术困难,并且这样的异常极易被察觉。设想苹果通过异或(XOR)或 Shamir 密钥共享等方式,将一个后门密钥与用户密钥组合:
- 实现层面的异常:用户设备在正常情况下应当能够独立完成解密/签名操作。如果加入隐藏密钥份额,意味着设备单凭用户自己的密钥无法完成某些解密,必须依赖苹果持有的那一份。这样的改动会造成额外的密钥协商步骤或异常的解密失败。例如,若苹果将后门密钥与用户密钥异或生成实际工作密钥,那么单用用户密钥将无法解密出正确结果,设备可能需要静默地向苹果服务器请求密钥片段或进行额外计算。这类非预期的通信或计算步骤很容易被安全研究者通过流量分析或逆向工程发现端倪。再比如采用 Shamir’s Secret Sharing 等门限方案,如果苹果持有一份密钥碎片,设备在解密时就需要满足门限条件,这通常意味着需要苹果的参与或预置公钥,从而在协议日志中留下异常痕迹。任何偏离常规协议的做法——无论是多传输一段数据,还是多保存一段密钥信息——都可能成为研究者捕捉的线索。历史经验表明,密码协议中的“奇怪之处”往往预示潜在漏洞或后门:例如 NSA 推出的 Dual_EC_DRBG 伪随机数生成器由于使用了异常常数,被专家迅速怀疑存在后门;著名密码学家施奈尔(Bruce Schneier)就曾直言 Dual_EC_DRBG 中的后门“相当明显”,呼吁业界停止使用en.wikipedia.org。由此可见,试图暗中插入额外密钥会在数学实现上留下破绽,而资深密码学者和安全社区有足够能力识别这些反常之处。
进一步,从门限签名理论对比苹果现有密钥管理,可以加深这一不可行性的理解。门限密码学允许将密钥拆分给多方持有,只有达到预定门槛的份额才能重构密钥或执行签名解密toc.csail.mit.edumedium.com。其优点在于提高了密钥托管的安全性,需要多方协作才能解锁秘密。然而,这种机制是公开设计的一部分,各参与方和流程都是明示的。例如在某些区块链多重签名方案中,多个私钥持有者共同生成交易签名,每个人都知晓门限机制的存在。相较之下,苹果在产品中的密钥管理要么是完全由用户端掌握密钥(如iPhone本地数据加密,密钥存在Secure Enclave中),要么是在用户许可下由苹果代管(如传统iCloud云备份未启用高级加密时,苹果保存备份密钥)。苹果并没有公开采用“两方门限”的模式来和用户分享密钥,否则等于声明“用户单方无法完全掌控自己的解密权”。如果苹果暗中采用门限签名让自己持有一份密钥碎片,本质上就是一种**变相密钥托管(Escrow)**行为。这样的做法会明显偏离苹果宣称的零后门立场,与其在隐私政策中反复强调的原则相违背。值得注意的是,苹果在其官方隐私声明中明确表示:“我们从未在任何产品或服务中创建过后门或万能解锁主密钥”apple.com。因此,从理论和实践双重层面来看,用户私钥与潜在后门密钥是难以在不被发现的情况下拆分存在的。任何试图将二者解耦的举措都会引起体系架构的异常,进而难逃专家法眼。
加密社区对后门的发现与审计
在当今的安全生态中,不存在“悄无声息的后门”。一旦厂商试图在加密方案中掺入后门密钥,全球的密码学社区和安全研究人员都有多种手段将其揪出。下面从几个方面概述社区常用的后门检测与审计方法:
-
开源协议分析:安全专家偏好开源的软件和协议,因为源码透明意味着任何可疑的算法修改、密钥处理流程都暴露在公众视野中。通过阅读和形式化分析公开的协议规范,研究者可以发现是否有多余的密钥交换步骤或异常的参数。例如,Signal通信协议的源代码和技术细节是完全公开的,全球专家曾多次审阅其实现,验证其端到端加密未存在后门linkedin.com。事实证明,公开透明带来的是更严苛的监督,任何隐秘加入的密钥参数都有可能被审计人员发现。正如业内人士所指出的,Signal 采用开放源码意味着安全专家可以独立审计其代码以核实安全性linkedin.com。类似地,许多现代加密库都会经过社区审视,以确保其中没有“暗门”。
-
逆向工程与二进制审计:对于闭源的软件(例如苹果自身的系统组件),安全研究者会运用逆向工程技术来分析应用的二进制代码和运行时行为。一旦苹果的加密实现存在未公开的密钥使用,比如在本地程序中引用了某个神秘常量或调用了隐藏的密钥解密函数,逆向工程往往能还原这些逻辑。专业团队通过调试、反编译、动态埋点等方式重现协议的握手过程,查看每一步骤所用的密钥材料。如果过程中出现与官方文档不符的环节(例如本应由用户设备生成的密钥却从外部获取),将立即引发怀疑。此外,安全社区定期举办的漏洞挖掘和破解挑战赛也扮演重要角色——顶尖黑客会竞相攻破苹果设备的加密层,并公开报告发现的问题。过去这些努力揭示了一些实现漏洞(如内存越界、0day攻击途径),但从未曝出“苹果预留万能密钥”之类的后门。一例典型事件是2017年有黑客成功解密了Secure Enclave固件以研究其中机理,结果证实即便取得固件代码,攻击者仍无法提取到任何用户密钥或后门凭证ciso.economictimes.indiatimes.com。这一结论进一步增强了业界对苹果加密实现中无后门的信心。
-
网络流量与协议行为分析:加密协议往往涉及设备与服务器的交互流程。研究人员会抓包和监控这些网络流量,分析协议握手时交换的消息格式和内容。如果苹果尝试在密钥协商时暗中插入自己的公钥或请求额外数据,流量分析将捕捉到异常的报文模式。例如,在正常的端到端加密通信中,设备之间交换彼此的公钥证书,不应有第三方公钥悄然出现。而所谓“幽灵用户”后门提案正是要求服务提供商在群聊中偷偷加入一个看不见的第三方公钥。这样的方案被广泛批评因为它破坏了用户验证通信对端身份的机制,需要服务器隐藏通知才能欺骗用户lawfaremedia.org。密码学家指出,这将削弱认证过程并带来新漏洞,因此难以在不被发现的情况下实施lawfaremedia.org。由此可见,通过流量异常识别潜在后门是切实可行的。当年的GCHQ“幽灵用户”建议一提出,就被包括苹果在内的业界联合抵制,47家机构和专家联名公开信指出该做法“对网络安全构成严重威胁”internetsociety.orgsilicon.co.uk,可见社区对这类后门手段有高度警惕性。
-
独立审计和信任链验证:许多安全敏感的加密功能会接受独立机构的审计,以建立公众信任。比如苹果的 iCloud 钥匙串(Keychain) 采用多层加密和信任链机制,其设计文档表明敏感信息的密钥始终需要Secure Enclave参与才能解锁techrepublic.com。有第三方评估指出,钥匙串中的私密数据即便保存在云端也是经过高强度加密的,任何人(包括苹果)都无法直接读取明文techrepublic.com。这一架构经过多轮外部安全会议研讨和学者研究,至今未出现被植入后门的迹象。同样,苹果设备中的 Secure Enclave 安全隔区 也多次成为学术研究和黑客大会的焦点。研究人员通过攻击Secure Enclave找出了少数漏洞(例如早期A7-A11芯片存在硬件级漏洞ciso.economictimes.indiatimes.comciso.economictimes.indiatimes.com),但这些漏洞只是实现瑕疵,并非有意留出的后门。实际上,正是这些公开的审计和破解挑战证明了Secure Enclave的设计初衷:即使攻击者获得硬件或固件访问权,仍无法提取出主密钥ciso.economictimes.indiatimes.com。学术界和白帽黑客社区通过反复的审查和渗透测试,为苹果的“零后门”承诺提供了有力的背书。换言之,加密社区的独立审计机制确保了任何后门都难以隐藏;只有经得起各方检验的系统,才能真正赢得用户信任。
综上所述,在强大的社区监督下,任何后门密钥的存在都会留下蛛丝马迹,并最终被曝光。无论是协议分析、逆向工程还是实网监测,多层次的手段使得厂商无法神不知鬼不觉地在成熟加密方案中藏入后门。这也是为什么苹果等公司反复强调没有后门:一旦撒谎,终将被揭穿,信用荡然无存。
iCloud 钥匙串信任链下的全局数据加密密钥(DEK)机制研究
苹果的高级数据保护(Advanced Data Protection)引入了端到端加密,将大部分 iCloud 数据的密钥仅存储在用户的受信设备上support.apple.com。在该机制下,每个用户的 iCloud 帐户针对各数据类别生成自己的“全局”数据加密密钥(Data Encryption Key, DEK),这些密钥受 iCloud 钥匙串的信任链机制保护。下面将详细探讨全局 DEK 的生成、分发与封装,多设备场景下的生命周期变化,以及苹果保障 DEK 安全和确保服务器从未获取明文 DEK 的技术手段。
全局 DEK 的生成、更新与轮换
初始生成:当用户首次在支持的设备上启用高级数据保护时(需运行 iOS 16.2、macOS 13.1 等新版系统,并开启双重认证),系统会在该设备上本地生成全局数据加密密钥。实际上,每个受端到端加密保护的 iCloud 服务(例如云备份、照片、笔记等)都有各自的 CloudKit 服务密钥对,其私钥用作该类别数据的主加密密钥support.apple.comsupport.apple.com。这些服务密钥使用安全随机算法在用户受信设备上创建,具有唯一性,并由设备的安全硬件保护。启用高级数据保护时,设备会将之前由苹果保存的云端密钥从苹果的硬件安全模块(HSM)中删除,并生成新的服务密钥,以改用仅存储在用户设备上的密钥来加密云端数据support.apple.comsupport.apple.com。这一过程确保全局 DEK(即各服务的新密钥)仅存在于用户受信设备上,苹果服务器端不再持有其副本。
是否变化及何时变化:在正常使用中,全局 DEK(各服务密钥)的私钥一经生成会保持稳定,用于持续加密解密用户数据,并不会频繁更换。唯有在特定事件下才会轮换或更新密钥,例如用户启用高级数据保护时系统触发的一次性密钥轮换,以及用户后来关闭高级数据保护或怀疑密钥泄露时的情况support.apple.com。苹果文档指出,当用户打开高级数据保护时,设备会启动异步密钥轮换操作,为此前存储于苹果服务器的每个服务创建新的服务密钥support.apple.com。新数据随后使用新密钥加密,旧密钥无法解密新数据support.apple.com。同样地,当用户关闭高级数据保护返回标准保护时,设备会将原本仅存于本地的新密钥上传回苹果HSM,并可恢复使用先前的旧密钥support.apple.com。因此,可以总结:初始启用高级保护时会生成并切换到新的全局 DEK,此后这些密钥保持不变;如用户关闭功能则恢复旧密钥;除非再次启用或发生安全事件,系统通常不会主动更换全局 DEK。
值得注意的是,在极端情况下如果用户怀疑密钥泄露或设备失窃,用户可以选择通过重置整个端到端加密环境(例如先关闭再重新开启高级数据保护)来触发新的 DEK 生成,从而保护云端数据安全。然而,此操作会要求所有设备重新加入信任链,并重新上传数据副本加密后存储。
多设备环境下 DEK 的分发与封装
信任链机制: 苹果使用 iCloud 钥匙串的信任链(又称同步圈,circle of trust)来在多设备间安全同步全局 DEK。启用了高级数据保护后,属于用户 Apple ID 的所有受信设备共同构成一个加密信任链,每台设备都有一对用于同步的非对称椭圆曲线密钥(如 P-384)support.apple.com。当第一台设备生成全局 DEK 后,它会将这些密钥加入自身的 iCloud 钥匙串保护域,并通过 CloudKit 安全地共享给用户的其他设备support.apple.com。具体而言,设备会维护一份受信设备的公钥列表,并使用自身的私钥对列表签名后存储于 iCloud;只有持有用户账户密码或设备私钥者才能读取或篡改这份列表support.apple.com。这一机制保证了只有经过用户授权加入信任链的设备才能获取 DEK,其余任何第三方(包括苹果服务器)都无法读取信任链中的密钥数据support.apple.com。
密钥传递与封装:在多设备场景下,每台设备都会持有全局 DEK(各服务私钥)的一个副本,但这些副本始终以安全加密形式封装后再传输和存储。例如,当用户新增一台受信设备时,新设备会生成自己的同步密钥对并向云端发出加入信任链的请求support.apple.com。已有的一台受信设备(通常是用户主动在其上同意新增设备)会验证该请求并通过 设备间安全信道 传输 DEK 副本给新设备support.apple.com。在此过程中,现有设备会利用新设备的公钥来加密封装 DEK,或双方通过椭圆曲线 Diffie-Hellman(ECDH)协商会话密钥来传递 DEK,从而确保只有目标新设备能解开密钥包装。苹果未公开具体用哪种算法封装,但业界常用方案包括 AES 密钥封装算法(AES-KW) 或 AES-GCM 算法 对会话密钥加密support.apple.comsupport.apple.com。可以推测,Apple 采用了符合 NIST 标准的 AES-256 算法对对称 DEK 进行二次加密包装,并结合设备的非对称密钥进行密钥交换/加密,以实现端到端的安全传递。
本地存储与保护:当设备接收到封装的 DEK 后,会在本地将其解密并安全保存于设备的 Keychain 中。所有 DEK 私钥仅存在于设备的安全隔区中,例如 iPhone 的密钥保存在 Data Protection 类钥匙串项下,并受 Secure Enclave 协处理器保护(访问需通过用户设备解锁)support.apple.com。这样设计保证即使设备遗失或被攻破,未解锁状态下设备上的 DEK 依然难以提取。总之,多设备环境下,每台受信设备都持有全局 DEK 副本,但始终通过端到端加密的方式同步与存储:传输过程中使用公钥加密/会话密钥,存储时依赖设备硬件密钥封装技术(如 Secure Enclave 提供的UID派生密钥)进一步加密,最大程度降低密钥泄露风险。
设备新增、移除与丢失场景下 DEK 和数据的生命周期
新设备加入: 当用户在新设备上登入 iCloud 并启用高级数据保护时,该设备无法直接访问云端受保护数据,需要首先加入信任链。加入流程包括:新设备生成自己的同步密钥对并将公钥提交给苹果云端(CloudKit)support.apple.com;苹果服务器将此请求传达给用户已有的一台受信设备上,提醒用户有新设备申请加入。用户在已有设备上批准请求(需输入密码或通过生物识别验证身份),之后已有设备会将新设备的公钥添加到信任链并再次用自己的私钥和账户密码派生密钥签署信任圈数据support.apple.com。随后,该已有设备通过上述安全信道,将全局 DEK 的加密副本传送给新设备support.apple.com。一旦新设备成功解密获得 DEK,它就加入了受信设备列表,可以像其他设备一样解密云端的端到端加密数据。整个过程确保只有获得用户明示批准的新设备才能获取 DEK support.apple.com。
设备移除与更换:当用户从 Apple ID 中移除某台设备,或设备被抹除/重置时,该设备将不再被视为信任链的一员。此时其他仍在线的受信设备会更新信任链状态,将该设备的身份从受信列表中剔除support.apple.com。需要强调的是,移除设备本身并不会导致全局 DEK 自动更改。被移除的设备虽曾持有 DEK 副本,但一旦不再受信,其无法从苹果服务器获取新的数据更新,而且由于设备已从账户移除或被抹掉,攻击者无法再借此解密云端后续的数据。苹果并未设定在每次设备变动时轮换密钥,这是出于实用性的考虑——频繁更换 DEK 将要求对云端大量数据重新加密,代价高昂。不过,若某台设备遗失且用户怀疑其本地密钥可能泄露,用户可以选择手动采取措施,例如从 iCloud 设置中移除此设备并重置高级数据保护(关闭再开启),从而生成新的 DEK,保护未来的数据安全。
云端数据影响: 当设备移除或失效时,云端已经加密的数据依旧由原来的 DEK 保护,并不会因为设备离开而重新加密。只要用户其他任一受信设备仍保存着该 DEK,便可继续访问此前的数据。被移除的设备由于缺失信任凭证,也无法再从服务器同步到后续新增或修改的任何机密数据(即使攻击者拥有其物理设备,由于密钥受 Secure Enclave 和设备密码保护,也难以提取support.apple.com)。因此,在多设备环境中,云端数据的可访问性取决于至少有一台受信设备存有对应 DEK。只要用户至少有一台设备或有效的恢复方式,数据就可解密使用;反之则数据陷于加密状态无法读取。
失去所有设备:高级数据保护要求用户在失去所有受信设备的极端情况下,借助预先设置的恢复机制取回 DEK。苹果强制要求启用该功能的用户提供至少一种账户恢复方法(例如指定恢复联系人或设置恢复密钥)support.apple.comsupport.apple.com。当用户所有设备均遗失或不可用时,只有通过这些恢复方式才能重获对数据的访问权。具体而言,如果用户提前设置了恢复密钥(一串随机生成的28位字符)并安全保存,那么此时用户可在新设备上登陆 Apple ID,并输入该恢复密钥来恢复数据。苹果服务器会将一份加密的 DEK 备份( escrow 记录 )下发到新设备,而新设备利用用户提供的恢复密钥将其解密,提取出全局 DEKsupport.apple.comsupport.apple.com。由于恢复密钥是由用户掌控、苹果不存储明文的要素,只有提供正确密钥的新设备才能解开 escrow 获得 DEK。在成功恢复后,新设备将重建信任链,并可以访问之前端到端加密的所有云端数据。
若用户选择的是恢复联系人,流程类似:用户联系预先设定的可信联系人,由联系人通过其苹果设备生成一个验证代码提供给用户。用户在新设备上输入该代码后,苹果同样将加密的 DEK 备份下发,新设备据此恢复密钥。整个恢复流程依然遵循端到端加密原则:苹果仅充当中转并验证权限,但并不知晓用户的实际 DEK 内容support.apple.com。
不可恢复的情况:如果用户既没有其他受信设备、又未设置任何恢复联系人或恢复密钥,那么全局 DEK 将无法找回,相应的云端数据也就永久处于加密不可读状态support.apple.com。苹果明确表示,若用户丢失所有设备且无恢复方式,公司无法帮助用户恢复这部分端到端加密的数据support.apple.com。这凸显了高级数据保护的一个权衡:安全性增强的同时,数据恢复的责任完全由用户自担。因此用户需谨慎管理受信设备和恢复选项,以避免陷入无法解密个人数据的境地。
DEK 安全性的密码学保障机制
苹果在高级数据保护与 iCloud 钥匙串架构中运用了多种密码学机制来保障 DEK 的机密性和完整性,包括密钥封装、密钥派生、硬件安全模块,以及严格的权限控制:
-
端到端加密与密钥层级化:如上所述,iCloud 采用分层密钥架构对数据加密。以 CloudKit 私有数据库为例,每位用户有一个顶层的 CloudKit 服务密钥对,其私钥用来保护下层对称密钥(如 Zone密钥、Record记录密钥等)
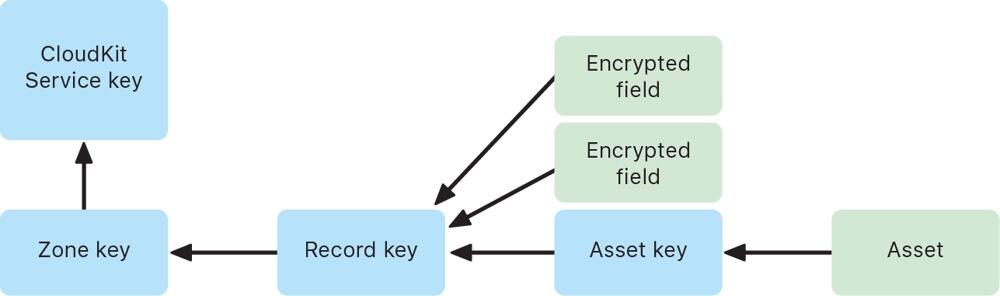 support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。
support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。 -
AES 密钥封装与封闭式硬件存储:苹果广泛采用了经验证的对称加密算法来封装和存储 DEK。传输过程中的 DEK(或下层对称密钥)通常通过 AES-256 算法加密封装后再上传support.apple.com。一种常用方法是 AES 密钥包装 (AES-KW),它专门用于用一个对称密钥安全地封装另一个密钥,确保密钥材料在传输中不暴露。与此同时,设备本地的 DEK 私钥会存储在受 Secure Enclave 保护的区域。Secure Enclave 为每台设备提供唯一的硬件 UID 密钥,仅用于解锁设备密钥袋和钥匙串项support.apple.com。也就是说, DEK 私钥本身可能被进一步用设备硬件密钥加密(这相当于在软件密钥之外又加了一道硬件锁)。只有当用户解锁设备并通过身份验证,操作系统才能调用 Secure Enclave 解封这些密钥用于加解密操作。通过AES-GCM 等对称加密结合Secure Enclave 硬件密钥封装,苹果确保 DEK 无论在云端传输还是本地存储,都始终处于加密状态,降低被截获或提取的风险support.apple.com。
-
椭圆曲线密码与密钥交换: 信任链中设备互认和密钥共享依赖椭圆曲线密码算法。每台设备的同步身份密钥对采用强大的 P-256 或 P-384 曲线support.apple.comsupport.apple.com。当新设备加入时,已有设备会利用椭圆曲线数字签名算法 (ECDSA) 对信任链数据签名校验,防止伪造support.apple.com。同时,在设备间传输 DEK 时,可能使用椭圆曲线 Diffie-Hellman (ECDH) 来建立共享密钥,加密传输内容。ECDH 可确保即使通信被窃听,攻击者无法推导出会话密钥,因而无法获取密钥内容。综上,非对称加密和密钥交换协议保证了只有合法设备才能参与密钥同步,新设备的引入需要现有设备用其私钥签名确认,杜绝中间人攻击或伪造信任链的可能。
-
密钥派生函数 (KDF):在某些步骤中,苹果使用了密钥派生函数强化密码。历史上,iCloud 钥匙串曾要求用户设置 iCloud 安全码时,将用户密码通过 PBKDF2 等KDF算法派生出密钥,用于签名和加密信任圈hackmag.comhackmag.com。即便在新的双重认证架构下,某些场景仍可能涉及KDF——例如恢复密钥或联系人代码很可能通过 KDF 转换为实际用于解密 escrow 密文的密钥材料。这些 KDF 算法引入高强度的盐值和大量迭代运算hackmag.com,增强了抗暴力破解能力,防止弱口令被攻击者猜测。总之,KDF 的应用确保从用户口令/恢复码到加密密钥的映射具有单向性和计算复杂度,进一步保护 DEK 相关流程的安全。
服务器无权获取明文 DEK 的保障
苹果的设计宗旨是在云端架起“盲墙”,确保服务器既无权也无实能接触用户 DEK 的明文,这也是实现“即使云端泄露,用户数据仍安全”的关键:
-
密钥仅存在于用户端: 开启高级数据保护后,所有主要 iCloud 数据类别的加密密钥仅存储于用户受信设备(或用户掌握的恢复载体)中,苹果服务器端不再保存这些密钥support.apple.com。文档明确指出,启用该功能后,苹果“无法读取或访问用户的服务密钥”support.apple.com。即在正常运行过程中,苹果的云服务器从未拥有解锁用户端到端加密数据所需的密钥。服务器所见到的只是由用户设备加密后的数据碎片,对其而言是不可解密的黑箱。
-
云端存储密文及加密元数据:iCloud 服务器虽然需要存储用户数据(如云照片、备忘录的加密内容),但这些内容均已由设备使用 DEK 加密完成。即便是为了提供某些功能,云端保留了少量未加密的元数据(如文件校验和用于重复数据消除),这些元数据也不包含可用于推导 DEK 的信息support.apple.comsupport.apple.com。苹果正在致力于将更多此类元数据也纳入端到端加密范围,以进一步减少明文暴露面support.apple.com。此外,CloudKit 框架要求开发者在模式中明确标记需要加密的字段,未标记的字段(例如排序用的时间戳)即便明文存储,亦不涉及敏感内容support.apple.com。由此,云服务器始终缺乏关于 DEK 或用户敏感数据的明文,一旦发生数据泄露或内部越权,攻击者拿到的也只是高强度加密下的乱码。
-
权限架构防范后门访问:苹果构建的信任链机制也防止了服务器假借授权来获取密钥的可能性。服务器不能私自添加受信设备或篡改信任链,因为每次信任链更新都需要现有设备的私钥签名以及(在老架构下)用户密码派生密钥的二次签名hackmag.comsupport.apple.com。苹果服务器既不持有用户设备私钥,也不知晓用户密码,因此无法伪造这些签名来诱导其他设备信任一个恶意设备。即使在双重认证体系下,服务器在设备加入流程中充当中继,并没有能力绕过用户批准直接将新设备植入圈内support.apple.comsupport.apple.com。这种架构等于为服务器访问用户密钥设置了密码学上的禁区。正如苹果安全白皮书所言,在最坏情形下如果用户丢失对 iCloud 钥匙串和其恢复机制的访问,那么相应的端到端加密数据苹果也无力恢复support.apple.com。苹果通过制度和技术结合,确保即便政府或机构要求提供用户数据,由于公司本身并无解密能力,只能交出加密的内容。
综上所述,Apple 高级数据保护下,全局数据加密密钥的生成由用户设备掌控,借助 iCloud 钥匙串信任链在多设备间安全同步。无论是在设备增加、移除还是用户失去设备的情况下,密钥和数据的生命周期管理均以用户掌控为中心:只要用户保有至少一个密钥载体(设备或恢复方式),数据即可解密使用;反之苹果也无法绕过用户获取密钥明文support.apple.com。苹果通过成熟的加密算法(AES-KW、ECDH 等)、硬件支持(Secure Enclave)、密钥分层与派生策略,实现了“零信任”云存储:服务器对用户密钥一无所知,从而使用户云端数据获得前所未有的保密性提升。
附录
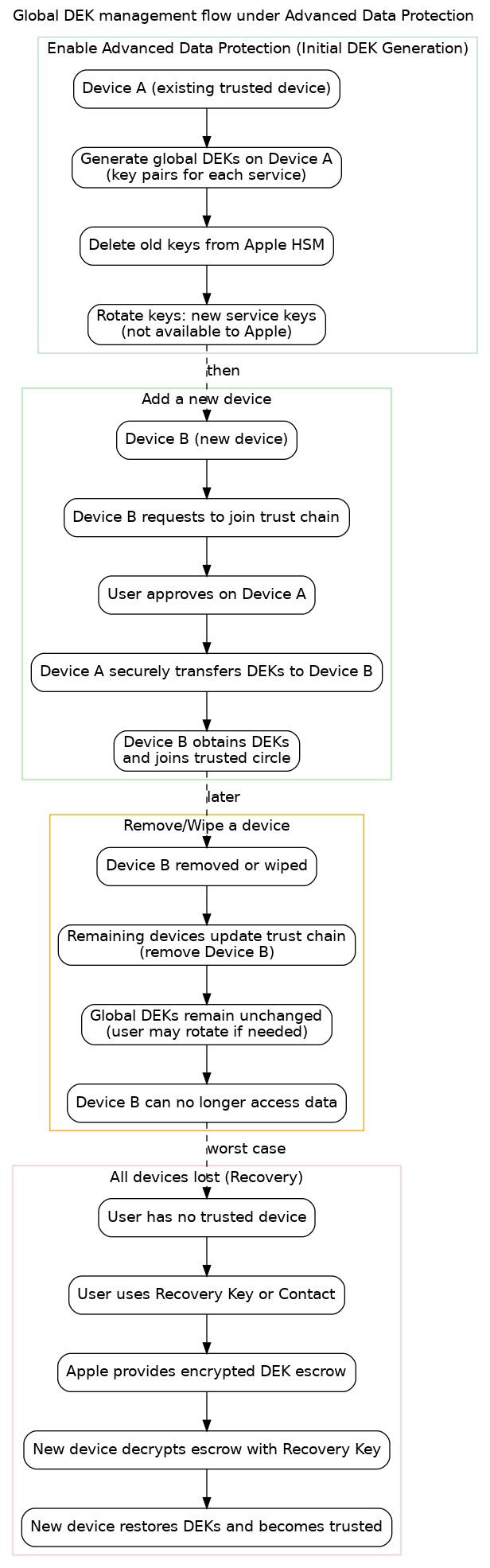 图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。
图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。 -
-
 @ 5f078e90:b2bacaa3
2025-05-18 18:47:21
@ 5f078e90:b2bacaa3
2025-05-18 18:47:21Sloth test
Just a test
Please ignore.

In the lush canopy of a rainforest, Sid the sloth hung lazily from a branch, his mossy fur blending with the leaves. Each day, he nibbled on tender shoots, moving so slowly that ants marched faster. One morning, a curious toucan dropped a shiny berry. Sid, intrigued, reached for it over hours, only to find it was a pebble! Chuckling, he napped, dreaming of sweeter finds. His unhurried life taught the jungle: patience brings its own rewards. (376 characters)