-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note
-
 @ 8fb140b4:f948000c
2023-07-22 09:39:48
@ 8fb140b4:f948000c
2023-07-22 09:39:48Intro
This short tutorial will help you set up your own Nostr Wallet Connect (NWC) on your own LND Node that is not using Umbrel. If you are a user of Umbrel, you should use their version of NWC.
Requirements
You need to have a working installation of LND with established channels and connectivity to the internet. NWC in itself is fairly light and will not consume a lot of resources. You will also want to ensure that you have a working installation of Docker, since we will use a docker image to run NWC.
- Working installation of LND (and all of its required components)
- Docker (with Docker compose)
Installation
For the purpose of this tutorial, we will assume that you have your lnd/bitcoind running under user bitcoin with home directory /home/bitcoin. We will also assume that you already have a running installation of Docker (or docker.io).
Prepare and verify
git version - we will need git to get the latest version of NWC. docker version - should execute successfully and show the currently installed version of Docker. docker compose version - same as before, but the version will be different. ss -tupln | grep 10009- should produce the following output: tcp LISTEN 0 4096 0.0.0.0:10009 0.0.0.0: tcp LISTEN 0 4096 [::]:10009 [::]:**
For things to work correctly, your Docker should be version 20.10.0 or later. If you have an older version, consider installing a new one using instructions here: https://docs.docker.com/engine/install/
Create folders & download NWC
In the home directory of your LND/bitcoind user, create a new folder, e.g., "nwc" mkdir /home/bitcoin/nwc. Change to that directory cd /home/bitcoin/nwc and clone the NWC repository: git clone https://github.com/getAlby/nostr-wallet-connect.git
Creating the Docker image
In this step, we will create a Docker image that you will use to run NWC.
- Change directory to
nostr-wallet-connect:cd nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - The last line of the output (after a few minutes) should look like
=> => naming to docker.io/library/nwc:latest nwc:latestis the name of the Docker image with a tag which you should note for use later.
Creating docker-compose.yml and necessary data directories
- Let's create a directory that will hold your non-volatile data (DB):
mkdir data - In
docker-compose.ymlfile, there are fields that you want to replace (<> comments) and port “4321” that you want to make sure is open (check withss -tupln | grep 4321which should return nothing). - Create
docker-compose.ymlfile with the following content, and make sure to update fields that have <> comment:
version: "3.8" services: nwc: image: nwc:latest volumes: - ./data:/data - ~/.lnd:/lnd:ro ports: - "4321:8080" extra_hosts: - "localhost:host-gateway" environment: NOSTR_PRIVKEY: <use "openssl rand -hex 32" to generate a fresh key and place it inside ""> LN_BACKEND_TYPE: "LND" LND_ADDRESS: localhost:10009 LND_CERT_FILE: "/lnd/tls.cert" LND_MACAROON_FILE: "/lnd/data/chain/bitcoin/mainnet/admin.macaroon" DATABASE_URI: "/data/nostr-wallet-connect.db" COOKIE_SECRET: <use "openssl rand -hex 32" to generate fresh secret and place it inside ""> PORT: 8080 restart: always stop_grace_period: 1mStarting and testing
Now that you have everything ready, it is time to start the container and test.
- While you are in the
nwcdirectory (important), execute the following command and check the log output,docker compose up - You should see container logs while it is starting, and it should not exit if everything went well.
- At this point, you should be able to go to
http://<ip of the host where nwc is running>:4321and get to the interface of NWC - To stop the test run of NWC, simply press
Ctrl-C, and it will shut the container down. - To start NWC permanently, you should execute
docker compose up -d, “-d” tells Docker to detach from the session. - To check currently running NWC logs, execute
docker compose logsto run it in tail mode add-fto the end. - To stop the container, execute
docker compose down
That's all, just follow the instructions in the web interface to get started.
Updating
As with any software, you should expect fixes and updates that you would need to perform periodically. You could automate this, but it falls outside of the scope of this tutorial. Since we already have all of the necessary configuration in place, the update execution is fairly simple.
- Change directory to the clone of the git repository,
cd /home/bitcoin/nwc/nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - Change directory back one level
cd .. - Restart (stop and start) the docker compose config
docker compose down && docker compose up -d - Done! Optionally you may want to check the logs:
docker compose logs
-
 @ e034d654:ca919814
2025-01-22 23:14:27
@ e034d654:ca919814
2025-01-22 23:14:27I stumbled into nostr end of March 2023. At that point already fully thrown into the hows, whys and whats of Bitcoin, never really interested in social apps, just recently playing around with Lightning, the only experience of which at the time was Muun (😬) and stacker.news custodial wallet.
Fairly inexperienced with technicals other than rough understandings of concepts. A crappy laptop node with a dangling SSD via USB, constantly having to resync to current blockheights whenever I was ready to make an on chain transaction to cold storage. My great success after over two years of delay, and a couple failed attempts.
Something about the breadth of information for nitty gritty specifics, the clash with all the things that I found interesting about Bitcoin, with others equally as focused, kept me interested in Nostr. Plus the lighthearted shit posting to break up plumbing the depths of knowledge appealed to me.
Cut to now. Through the jurisdictional removals and even deaths of LN wallet projects, using mobile LSPs, finding use cases with the numerous cashu implementations, moderate comfortability with NWC strings of various permissions, budgets for seemingly endless apps of Nostr clients, swapping relays, isolated wallets with Alby go for my wife and cousin (I told them both not to put much on there as I'm sure failure is imminent) Alby Hub and Zeus, now fully backended by my own persistently online lightning node. All of it adding to the fluidity of my movement around the protocol.
Nimble.
Gradual progress. Reading through notes and guides posted on Nostr learning little bits, circling back eventually, if even at a time it wasn't clicking for me. Either way. Glad i've stuck to it even if I still barely know what it is I'm doing.
-
 @ d57360cb:4fe7d935
2025-01-22 22:58:31
@ d57360cb:4fe7d935
2025-01-22 22:58:31Time sinks and energy wastage.
The topic I'd like to talk on is being worse at something you do when you think about it doing it. Not even overthinking about it, but just in general thinking about an action. Becoming aware and self-conscious seems to divide you. Almost like splitting your brain and body in two when they should be working as a unit. Why am I worse when I want to do better?
The issue of multitasking
Why does my game at any sport or activity take a fall when I begin to think endlessly about it? We can’t multitask; our brain thrives on focus, pure focus. Laser-like unwavering — that’s when the mind is at its best. The kind of focus you have when you are thoughtless, when there is no self present. When you and the activity are merged as one, you reach a state where there is no longer activity, and there is no longer the human participating in the activity. This has been known to be zen, the Tao, the way, Wu Wei, and the flow state. It seems to me when one thinks about an action and simultaneously performs the action, they are experiencing a split in attention.
Trust your natural creativity
An action done without thought is smooth, unfiltered, and untainted by mental precepts for how it should’ve been carried out. Our bodies are natural and know better than our brains. Even as I write this, my best sentences and writing come from when I’m simply not thinking about them. But why? Simply because you allow the genius of creativity to flow through unobstructed. When you analyze and overthink, you get in your own way; you misdirect your energy, you split your brain and body, and you get them out of alignment.
We are at our best when we do one thing at a time, fully attentive, yet should not be mistaken for thinking about being attentive one must be fully there, where there is no thought. There is no mental chatter or storytelling; all flows like a vicious, violent river. These are inherent gifts, spontaneous like nature. The birds don’t think to fly, the plants don’t think to sprout, yet they create the most jaw-dropping beauty. Why do you think you are above that?
Trust your nature; trust your gift. Allow patience to carry you through.
-
 @ 16d11430:61640947
2025-01-22 22:28:44
@ 16d11430:61640947
2025-01-22 22:28:44In this article, we—an experienced social psychologist and a seasoned programmer—offer a dual perspective on the phenomenon of Bitcoin maximalism, the use of the term "shitcoin," and their relation to the savior complex. By combining psychological insights with technical expertise, we aim to provide a professional and nuanced analysis of this deeply polarizing cultural and technological movement.
The Rise of Bitcoin Maximalism
Bitcoin maximalism is a belief system centered on Bitcoin as the ultimate cryptocurrency. Its adherents, often referred to as "maxis," see Bitcoin not only as a superior technology but also as a solution to systemic issues such as financial inequality, corruption, and centralization. In contrast, alternative cryptocurrencies, pejoratively labeled as "shitcoins," are dismissed as fraudulent, unnecessary, or inherently inferior.
This binary worldview has profound psychological and social implications. It fosters tribalism, strengthens in-group cohesion, and positions Bitcoin as a near-messianic force. To understand this phenomenon, we must examine its roots in human psychology and its interplay with the principles of programming.
The Psychological Underpinnings of Bitcoin Maximalism
- Cognitive Dissonance and Reinforcement
Bitcoin maximalists often face critiques about Bitcoin's volatility, environmental impact, and scalability. To reconcile these challenges, many double down on Bitcoin’s virtues—decentralization, scarcity, and resilience—reinforcing their commitment to the ideology. This psychological mechanism, known as cognitive dissonance reduction, explains why contrary evidence often strengthens, rather than weakens, belief.
- In-Group/Out-Group Dynamics
The term "shitcoin" serves as a boundary marker, clearly delineating the in-group (Bitcoin supporters) from the out-group (altcoin proponents). By dismissing alternative cryptocurrencies in such stark terms, maxis reinforce group identity and loyalty while fostering hostility toward outsiders.
- The Savior Complex
A central element of Bitcoin maximalism is the belief that Bitcoin is humanity’s salvation from fiat corruption and economic oppression. This savior complex positions maxis as moral crusaders with an obligation to "convert" others to the Bitcoin ethos. Like religious evangelism, this belief system creates a sense of mission but also fosters black-and-white thinking, where dissenters are seen as either ignorant or malicious.
The Programmer’s Perspective: Technology and Tribalism
From a programmer’s standpoint, Bitcoin is an elegant solution to a specific set of problems. Its decentralized consensus mechanism, cryptographic security, and hard-capped supply make it an exceptional technological achievement. However, its success has unintentionally given rise to tribalism and ideological rigidity.
- Bitcoin’s Immutable Certainty
Programmers value systems that are deterministic and predictable, and Bitcoin embodies these principles. Its unchangeable supply of 21 million coins provides psychological comfort in a world of economic uncertainty. This technical feature aligns with human desires for stability and control, reinforcing maximalist beliefs.
- The Noise of Shitcoins
Altcoins, while occasionally innovative, are often poorly designed or exploitative projects. For developers, the term "shitcoin" reflects frustration with the proliferation of low-quality alternatives that dilute legitimate innovation. However, dismissing all altcoins under this label ignores the possibility that other projects may address use cases Bitcoin cannot efficiently solve.
- Savior Complex in Development Philosophy
Programmers often fall into the trap of believing their code or system is the ultimate solution to a problem. Bitcoin maximalism mirrors this mindset, elevating Bitcoin to a singular, untouchable status. While Bitcoin’s architecture is revolutionary, this perspective stifles the exploration of complementary technologies that could enhance the ecosystem.
Intersecting Psychology, Technology, and Ideology
The savior complex within Bitcoin maximalism emerges from a blend of psychological needs, technological admiration, and ideological fervor. This dynamic is sustained by:
Simplistic Narratives: Bitcoin is often framed as the hero in a battle against fiat corruption. The term "shitcoin" simplifies this narrative, casting altcoins as distractions or enemies.
Confirmation Bias: Maxis seek out information that supports their beliefs while dismissing contrary evidence, reinforcing their worldview.
Fear of Uncertainty: In an unpredictable world, Bitcoin offers a sense of security and moral clarity, making it easy to cling to as the "one true solution."
Balancing Ideology and Innovation
While Bitcoin maximalism has played a role in driving adoption and strengthening community, its rigid ideological framework risks stifling innovation. The derogatory dismissal of altcoins as "shitcoins" undermines constructive dialogue and the exploration of solutions that could complement Bitcoin’s capabilities.
As professionals in psychology and programming, we advocate for a balanced approach. Recognizing Bitcoin’s strengths does not require rejecting the potential of other technologies. Similarly, understanding the psychological roots of maximalism can help foster healthier, more inclusive discussions within the cryptocurrency space.
Conclusion
Bitcoin maximalism, the term "shitcoin," and the savior complex illustrate the complex interplay between human psychology and technological innovation. While Bitcoin’s architecture is a testament to programming ingenuity, its elevation to an ideological crusade reflects deeply ingrained cognitive and social behaviors.
By embracing nuance and humility, the cryptocurrency community can transcend tribalism and work collaboratively toward a decentralized future where technology serves humanity, not ideology. Only by balancing innovation with open-mindedness can we unlock the true potential of blockchain technology.
-
 @ c54f9c60:7c34249a
2025-01-22 22:12:51
@ c54f9c60:7c34249a
2025-01-22 22:12:51In October 2018, Arjun Balaji asked the innocuous question, What have you learned from Bitcoin? After trying to answer this question in a short tweet, and failing miserably, I realized that the things I've learned are far too numerous to answer quickly, if at all.
The things I've learned are, obviously, about Bitcoin - or at least related to it. However, while some of the inner workings of Bitcoin are explained, the following lessons are not an explanation of how Bitcoin works or what it is, they might, however, help to explore some of the things Bitcoin touches: philosophical questions, economic realities, and technological innovations.
The 21 lessons are structured in bundles of seven, resulting in three chapters. Each chapter looks at Bitcoin through a different lens, extracting what lessons can be learned by inspecting this strange network from a different angle.
Chapter 1 explores the philosophical teachings of Bitcoin. The interplay of immutability and change, the concept of true scarcity, Bitcoin's immaculate conception, the problem of identity, the contradiction of replication and locality, the power of free speech, and the limits of knowledge.
Chapter 2 explores the economic teachings of Bitcoin. Lessons about financial ignorance, inflation, value, money and the history of money, fractional reserve banking, and how Bitcoin is re-introducing sound money in a sly, roundabout way.
Chapter 3 explores some of the lessons learned by examining the technology of Bitcoin. Why there is strength in numbers, reflections on trust, why telling time takes work, how moving slowly and not breaking things is a feature and not a bug, what Bitcoin's creation can tell us about privacy, why cypherpunks write code (and not laws), and what metaphors might be useful to explore Bitcoin's future.
Each lesson contains several quotes and links throughout the text. If I have explored an idea in more detail, you can find links to my related works in the "Through the Looking-Glass" section. If you like to go deeper, links to the most relevant material are listed in the "Down the Rabbit Hole" section. Both can be found at the end of each lesson.
Even though some prior knowledge about Bitcoin is beneficial, I hope that these lessons can be digested by any curious reader. While some relate to each other, each lesson should be able to stand on its own and can be read independently. I did my best to shy away from technical jargon, even though some domain-specific vocabulary is unavoidable.
I hope that my writing serves as inspiration for others to dig beneath the surface and examine some of the deeper questions Bitcoin raises. My own inspiration came from a multitude of authors and content creators to all of whom I am eternally grateful.
Last but not least: my goal in writing this is not to convince you of anything. My goal is to make you think, and show you that there is way more to Bitcoin than meets the eye. I can’t even tell you what Bitcoin is or what Bitcoin will teach you. You will have to find that out for yourself.
"After this, there is no turning back. You take the blue pill —the story ends, you wake up in your bed and believe whatever you want to believe. You take the red pill— you stay in Wonderland, and I show you how deep the rabbit hole goes."
-
 @ ae6ce958:d0f02c7d
2025-01-22 22:09:59
@ ae6ce958:d0f02c7d
2025-01-22 22:09:59In a world increasingly reliant on software, ensuring its reliability, fairness, and ethical operation has never been more critical. Enter DamageBDD, a visionary platform combining Behavior-Driven Development (BDD) principles with the Bitcoin Lightning Network to create an inclusive, sustainable ecosystem that rewards contributors for enhancing global software quality. DamageBDD offers a groundbreaking solution: a decentralized, incentivized network where contributors can earn continuous rewards for their efforts, fostering collaboration, innovation, and resilience on a planetary scale.
A Global Network of Inclusion
One of DamageBDD's core strengths lies in its accessibility. The platform lowers barriers to participation, enabling individuals from all walks of life to contribute to software quality assurance. Whether you're a seasoned developer, a student exploring programming, or an enthusiast with logical reasoning skills, DamageBDD offers a place for you to thrive.
- Inclusivity Across Borders: No matter where contributors are located, they can participate, write tests, and verify implementations, earning Bitcoin payouts directly via the Lightning Network. This opens doors for individuals in underserved regions, empowering them to earn a sustainable income by contributing to a global digital infrastructure.
- Democratizing Software Development: By simplifying the process of writing and validating BDD test cases, DamageBDD ensures that anyone, regardless of technical background, can play a vital role in the ecosystem.
Sustainability Through Continuous Rewards
DamageBDD introduces a revolutionary incentive model where contributors earn not just for initial efforts but for the enduring utility of their work. Once a contributor writes and validates a test case or implements a feature, they can continue to earn payouts every time that test is executed successfully in the future. This model creates a self-sustaining loop of collaboration, innovation, and maintenance:
- Long-Term Incentives: Contributors remain financially motivated to keep their tests updated and ensure the associated feature works as expected. This continuous engagement ensures the software remains resilient, evolving to meet changing requirements.
- Encouraging Best Practices: By linking payouts to ongoing test executions, DamageBDD promotes robust test writing and feature development, reducing technical debt and encouraging sustainable software practices.
This approach not only aligns incentives with quality but also creates a virtuous cycle where contributors benefit from the long-term success of their work, ensuring a healthier, more collaborative software ecosystem.
Empowering Contributors for a Sustainable Future
Participating in the DamageBDD network provides contributors with opportunities that extend beyond monetary rewards. It empowers individuals and communities by fostering education, skill development, and global collaboration.
- Economic Empowerment: By earning Bitcoin payouts for their contributions, participants gain access to a global, borderless financial system. This is particularly impactful for those in regions with limited economic opportunities or unstable fiat currencies.
- Skill Development: Contributors learn and refine valuable skills, from writing precise BDD test cases to collaborating on complex software projects. These skills are transferable, increasing contributors' employability and confidence.
- Community Collaboration: The DamageBDD network brings together a diverse group of individuals and teams, creating a vibrant global community focused on innovation and quality.
A Self-Sustaining Software Ecosystem
At the heart of DamageBDD is a vision of a self-sustaining software ecosystem, where contributors, users, and developers are interconnected through mutual benefits:
- Decentralized Verification: Billions of test cases are verified daily on a distributed infrastructure, ensuring scalability and resilience.
- Dynamic Liquidity: The Bitcoin Lightning Network provides seamless micropayments, ensuring that contributors are rewarded in real time without delays or intermediaries.
- Adaptive Testing: DamageBDD's network detects gaps in coverage and autonomously generates new tests, keeping the ecosystem robust and up-to-date.
- Environmental Sustainability: By leveraging existing decentralized infrastructure and incentivizing efficient software development practices, DamageBDD minimizes waste and maximizes resource utilization.
The Ripple Effect: Continuous Benefits for All
As the DamageBDD ecosystem grows, its benefits extend far beyond individual contributors. Organizations, communities, and even nations stand to gain:
- For Organizations: High-quality software reduces downtime, builds user trust, and accelerates innovation. Companies that integrate with DamageBDD can leverage its robust test coverage to deliver better products faster.
- For Communities: DamageBDD creates local economic opportunities by enabling individuals to participate in the global digital economy. Communities can build localized solutions while tapping into a global network of expertise.
- For the Planet: A robust, well-tested software ecosystem reduces inefficiencies and ensures that digital infrastructure remains resilient in the face of global challenges.
A Vision for the Future
Imagine a world where billions of users collaborate daily to ensure the quality of the software we all rely on. In this vision, DamageBDD is the backbone of a planetary-scale ecosystem, verifying billions of tests and creating an ever-evolving foundation for innovation. Every test case is a building block, every contributor is a stakeholder, and every payout is a step toward a more equitable, sustainable, and inclusive digital future.
By aligning incentives with quality and participation, DamageBDD transforms software development into a collective endeavor that benefits everyone. It is more than a platform; it is a movement—one that empowers individuals, fosters collaboration, and builds a sustainable digital world for generations to come.
-
 @ c54f9c60:7c34249a
2025-01-22 21:48:30
@ c54f9c60:7c34249a
2025-01-22 21:48:30Falling down the Bitcoin rabbit hole is a strange experience. Like many others, I feel like I have learned more in the last couple of years studying Bitcoin than I have during two decades of formal education.
The following lessons are a distillation of what I’ve learned. First published as an article series titled “What I’ve Learned From Bitcoin,” what follows can be seen as a second edition of the original series.
Like Bitcoin, these lessons aren't a static thing. I plan to work on them periodically, releasing updated versions and additional material in the future.
Unlike Bitcoin, future versions of this project do not have to be backward compatible. Some lessons might be extended, others might be reworked or replaced. I hope that a future version will be something you can hold in your hands, but I don’t want to promise anything just yet.
Bitcoin is an inexhaustible teacher, which is why I do not claim that these lessons are all-encompassing or complete. They are a reflection of my personal journey down the rabbit hole. There are many more lessons to be learned, and every person will learn something different from entering the world of Bitcoin.
I hope that you will find these lessons useful and that the process of learning them by reading won’t be as arduous and painful as learning them firsthand.
nostr:npub1dergggklka99wwrs92yz8wdjs952h2ux2ha2ed598ngwu9w7a6fsh9xzpc
-
 @ 16d11430:61640947
2025-01-22 21:42:52
@ 16d11430:61640947
2025-01-22 21:42:52Greetings from the smoldering ruins of 2153. I come to you as a weary traveler, a programmer who survived the Great Shitcoin Implosion and the Genocide of the Staked. You might have called it "innovation" in your time. We call it hubris.
It started innocuously enough, as all human calamities do. Someone pitched an alternative consensus model—let’s call it "Proof of Destiny" or "Green-and-Fuzzy-Stake"—claiming it could scale faster than Proof of Work (PoW), use less energy, and, of course, “decentralize everything.” No one stopped to ask, “Decentralize what?” or “Decentralize how?” Humanity, in its infinite impatience, heard the siren song of infinite scalability and ran headlong into its own destruction.
The Bottleneck You Never Fixed
Here’s a secret from the future: entropy doesn't care about your buzzwords. Scalability is a thermodynamic problem, not just an engineering one. It turns out, there’s no magic math to sidestep the subatomic costs of validating state changes across a global network. With PoW, at least, the bottleneck is explicit: we expend energy to establish universal order. It’s painfully slow, yes, but incorruptible.
But Proof of Stake? The whole model was a stack of assumptions so fragile that quantum vibrations could collapse it. In fact, they did—literally. In 2124, when quantum computers were finally commercialized, it only took two weeks for a cabal of oligarchs to hijack 99% of all staked networks by manipulating randomness at an atomic level. Every "decentralized" ledger turned into a hyper-centralized ledger controlled by less than a dozen private keys. They called it The Great Reversal.
Trusting Consensus in the Hands of Kings
You fools thought PoS was democratic. You never understood that staking isn't decentralization; it's plutocracy in disguise. By the time you realize that "validator nodes" are just a euphemism for "central banks in denial," it’s already too late. You’ve created empires built on trustless systems that paradoxically require maximum trust in human operators.
From my vantage point in the scorched future, I watched it play out like a rerun of a bad sitcom: networks collapsing under Sybil attacks, validators bribing governments, entire populations disenfranchised because they couldn’t afford the buy-in. By 2135, staked systems became tools of oppression, no different from fiat empires. The world learned the hard way: when power isn’t grounded in physics, it’s grounded in tyranny.
Genocide on the Blockchain
Then came the genocides. Ah, yes, I promised you some dystopian gore. Imagine this: every individual’s identity, every asset, every shred of data tied to a staked ledger controlled by an exploitative minority. They called it "algorithmic efficiency." I called it a ledger of doom.
When the consensus broke, it wasn’t just money that disappeared. It was land ownership, healthcare records, citizenship data. Millions—no, billions—were erased from existence with the push of a button. And those lucky enough to survive? They were hunted, liquidated, and enslaved by the new "validator kings," whose power was cemented not by merit but by the sheer luck of having staked early.
They built gas chambers fueled by your carbon-neutral lies. Don’t worry, though—every execution was immutably recorded on-chain.
The Bitter Lesson: Physics Doesn’t Bend
You had one shot, humanity. Proof of Work was ugly, clunky, and energy-intensive, but it worked because it adhered to the most fundamental law of the universe: you cannot create order without expending energy. You could’ve embraced Bitcoin as the imperfect, honest system it was. Instead, you chased fantasies, selling your sovereignty for promises of infinite throughput and eco-friendliness.
You forgot that trustless systems must be rooted in objective reality. Proof of Stake? Proof of Reputation? Proof of Authority? All just trust models wrapped in cryptographic jargon. Your greed for "more" blinded you to the inevitability of centralization. And when the center collapsed, so did your world.
My Lament as a Survivor
I sit here now, in a bunker powered by scavenged PoW miners, writing this message to you, knowing full well you won’t listen. Humanity never does. The lessons are clear: Don’t scale beyond what physics allows. Don’t trust systems that abstract away energy costs. And for God’s sake, don’t trust humans to stay honest when they hold the keys to consensus.
Maybe you’ll prove me wrong. Maybe you’ll learn to embrace systems that prioritize resilience over convenience, decentralization over speed. Or maybe you’ll make the same mistake we did and pave the road to your extinction with staking rewards.
Either way, I’ll be here, in the radioactive wasteland, running a Bitcoin node. It's slow, yes—but at least it’s alive.
-
 @ a311301f:4663f8f2
2025-01-22 21:39:38
@ a311301f:4663f8f2
2025-01-22 21:39:38```perl
!/usr/bin/perl
use strict; use warnings; use Term::ReadKey;
STDOUT->autoflush(1);
this version run on Windows and use a pwd.txt file created by
the perl program ; otherwise encoding issue may follow
following sub needs to be used first by uncommenting the main call
sub write_password { print ("Enter Password: ") ; my $password =
; my $file_path = 'pwd.txt'; open(my $fh, '>', $file_path) or die "Cannot open file '$file_path' for writing: $!"; print $fh $password; close($fh); print ("\n"); print "Password written to '$file_path'\n"; } sub printhex { my $str = shift ; foreach my $char (split //, $str) { printf "%02x ", ord($char); } print "\n"; }
Function to read password from file
sub read_password_from_file { #unecessary #binmode(STDIN, ':crlf'); my $file_path = shift; #unecessary #local $/ = "\r\n" ; # CR, use "\r\n" for CRLF or "\n" for LF open(my $fh, '<', $file_path) or die "Cannot open file '$file_path' for reading: $!"; my $password = <$fh>; close($fh); #printhex ($password) ;
chomp($password); print "'$password'\n" ; #$password =~ s/\r?\n$//; # Remove newline character #$password = substr($password, 2) ; # BOM File starts with FF FE printhex($password ) ; # "\'$password\'\n" ; #$password = "abcde" ;
return $password; }Main program
sub main { #write_password(); # to uncomment for first use my $correct_password = read_password_from_file("pwd.txt") ; print "Enter password: "; ReadMode('noecho'); # Turn off echo my $entered_password = ReadLine(0); ReadMode('restore'); # Restore echo chomp($entered_password); print "\n";
# Compare entered password with the correct password if ($entered_password eq $correct_password) { print "Access granted!\n"; } else { print "Access denied!\n"; print "'$entered_password' not eq '$correct_password' \n"; printhex ($entered_password); printhex ($correct_password) ; print "The end! \n" ; }}
Call main function
main();
```
-
 @ 35f3a26c:92ddf231
2025-01-22 20:48:34
@ 35f3a26c:92ddf231
2025-01-22 20:48:34Background
Most people non familiar with Bitcoin thinks that there its has not smart contracts capabilities, and that is incorrect, there are smart contract capabilities, and despite limited in comparison with other blockchain networks, those capabilities are evolving slowly but surely.
The support for smart contracts is done through its scripting language, Script, which allows developers to create complex conditions for transactions.
What can you do with Script? 1. time locks 2. multi-signature requirements 3. other custom logic
opcodes like OP_CHECKLOCKTIMEVERIFY (CLTV) and OP_CHECKSEQUENCEVERIFY (CSV) are used to build more sophisticated smart contracts, these opcodes enable features such as the Lightning Network, a key scaling solution for Bitcoin
back in 2021, the Taproot upgrade introduced Pay-to-Taproot (P2TR), in summary allows for more private and efficient smart contracts, in that soft fork more was added, in addition to Taproot, we got as well Schnorr signatures, which enables multiple signatures to be aggregated into a single signature, improving scalability and privacy and MAST (Merklized Abstract Syntax Trees) which reduces the size of complex smart contracts, making them more efficient, as an added value, this efficiency reduces the cost of transactions.
The Taproot upgrade has laid the foundation for the development of more sophisticated smart contracts on the Bitcoin network, and the use of covenants is an important part of this development.
What is Bitcoin Covenants?
It is a BIP (Bitcoin Improvement Proposal), BIP-347, assigned on April 24, 2024, which marks the first step towards reintroducing functionality removed from Bitcoin by its creator Satoshi Nakamoto in 2010. This proposal aims to bring smart contract functionality to Bitcoin as we see in other EVM networks.
The proposal’s developers authors names are Ethan Heilman and Armin Sabouri, now the community will debate its merits.
Here the link, in case you are curious:
https://github.com/bitcoin/bips/blob/master/bip-0347.mediawiki
It is worth to read the motivation section of the BIP, which reads:
“Bitcoin Tapscript lacks a general purpose way of combining objects on the stack, restricting the expressiveness and power of Tapscript. This prevents, among many other things, the ability to construct and evaluate merkle trees and other hashed data structures in Tapscript. OP_CAT, by adding a general purpose way to concatenate stack values, would overcome this limitation and greatly increase the functionality of Tapscript.
OP_CAT aims to expand the toolbox of the tapscript developer with a simple, modular, and useful opcode in the spirit of Unix. To demonstrate the usefulness of OP_CAT below we provide a non-exhaustive list of some use cases that OP_CAT would enable:
Bitstream, a protocol for the atomic swap (fair exchange) of bitcoins for decryption keys, that enables decentralized file hosting systems paid in Bitcoin. While such swaps are currently possible on Bitcoin without OP_CAT, they require the use of complex and computationally expensive Verifiable Computation cryptographic techniques. OP_CAT would remove this requirement on Verifiable Computation, making such protocols far more practical to build in Bitcoin.
Tree signatures provide a multisignature script whose size can be logarithmic in the number of public keys and can encode spend conditions beyond n-of-m. For instance a transaction less than 1KB in size could support tree signatures with up to 4,294,967,296 public keys. This also enables generalized logical spend conditions.
Post-Quantum Lamport signatures in Bitcoin transactions. Lamport signatures merely require the ability to hash and concatenate values on the stack. [4] It has been proposed that if ECDSA is broken or a powerful computer was on the horizon, there might be an effort to protect ownership of bitcoins by allowing people to mark their taproot outputs as "script-path only" and then move their coins into such outputs with a leaf in the script tree requiring a Lamport signature. It is an open question if a tapscript commitment would preserve the quantum resistance of Lamport signatures. Beyond this question, the use of Lamport Signatures in taproot outputs is unlikely to be quantum resistant even if the script spend-path is made quantum resistant. This is because taproot outputs can also be spent with a key. An attacker with a sufficiently powerful quantum computer could bypass the taproot script spend-path by finding the discrete log of the taproot output and thus spending the output using the key spend-path. The use of "Nothing Up My Sleeve" (NUMS) points as described in BIP-341 to disable the key spend-path does not disable the key spend-path against a quantum attacker as NUMS relies on the hardness of finding discrete logs. We are not aware of any mechanism which could disable the key spend-path in a taproot output without a soft-fork change to taproot.
Non-equivocation contracts in tapscript provide a mechanism to punish equivocation/double spending in Bitcoin payment channels. OP_CAT enables this by enforcing rules on the spending transaction's nonce. The capability is a useful building block for payment channels and other Bitcoin protocols.
Vaults [6] which are a specialized covenant that allows a user to block a malicious party who has compromised the user's secret key from stealing the funds in that output. As shown in OP_CAT is sufficient to build vaults in Bitcoin.
Replicating CheckSigFromStack which would allow the creation of simple covenants and other advanced contracts without having to pre-sign spending transactions, possibly reducing complexity and the amount of data that needs to be stored. Originally shown to work with Schnorr signatures, this result has been extended to ECDSA signatures.
OP_CAT was available in early versions of Bitcoin. In 2010, a single commit disabled OP_CAT, along with another 15 opcodes. Folklore states that OP_CAT was removed in this commit because it enabled the construction of a script whose evaluation could have memory usage exponential in the size of the script. For example, a script that pushed a 1-byte value on the stack and then repeated the opcodes OP_DUP, OP_CAT 40 times would result in a stack element whose size was greater than 1 terabyte assuming no maximum stack element size. As Bitcoin at that time had a maximum stack element size of 5000 bytes, the effect of this expansion was limited to 5000 bytes. This is no longer an issue because tapscript enforces a maximum stack element size of 520 bytes.”
The last update of the BIP was done on Sep. 8 2024 by Ethan Heilman
Controversy
The controversy revolves around two main camps:
- Those who want to preserve Bitcoin’s network for monetary transactions only, arguing that adding smart contract capabilities could introduce risks and complexity.
- Others who advocate for expanding Bitcoin’s capabilities to support a wider range of applications, seeing OP_CAT as a step towards enhancing the network’s utility.
Final Thoughts
Bitcoin have done what no other asset have done in history, neither gold, its success is clear, and now, that BlackRock is involved, “miraculously”, corporations and governments are getting on board and Bitcoin is not anymore only for criminals or “rat poison” or “is going to zero”.
But as all tech, improvements are important, if those improvements are done to secure more the network and to make it more robust, there will be little to none controversy, however, when those changes are aiming at adding new shinning features that would change Bitcoin into a network with similar features as Ethereum in terms of contracts that requires attention and debate, few questions come to mind:
- How will that change affect the security of the network?
- How that change will affect the blockchain usage?
- What is the projected impact over the fees per transaction if this change is approved?
- Will the impact create pressure for the block size increase discussion to come back to the table and with it a second war?
Looking into Ethan Heilman work and contribution to the Bitcoin ecosystem, I am inclined to believe that he has considered most of those questions.
Looking forward to observe the evolution of this proposal.
You liked the article? Make my day brighter!
Like and share!
Last but not least, the following link is an unstoppable domain, it will open a page in which you can perform an anonymous contribution to support my work:
https://rodswallet.unstoppable/
The link didn’t open?
To open the link you need to use a best in class browser that supports web3, two are recommended: Brave Browser and Opera Browser
-
 @ f33c8a96:5ec6f741
2025-01-22 20:38:02
@ f33c8a96:5ec6f741
2025-01-22 20:38:02 -
 @ bf47c19e:c3d2573b
2025-01-22 19:14:55
@ bf47c19e:c3d2573b
2025-01-22 19:14:55PREUZMITE ODLOMAK
KUPITE ELEKTRONSKO IZDANJE KNJIGE
Autor: Natanijel Poper
Prevodilac: Nevena Andrić
Kako funkcioniše novac, ko iz njega izvlači korist i kako bi sve to moglo izgledati ubuduće.
Bitkoin, revolucionarna digitalna valuta i finansijska tehnologija, predstavlja začetak jednog globalnog društvenog pokreta utopijskih stremljenja. Ideja nove valute, koju održavaju personalni računari širom sveta, bila je predmet brojnih šala, ali to je nije sprečilo da preraste u tehnologiju vrednu više milijardi dolara, tehnologiju s mnoštvom sledbenika, koji je smatraju najvažnijim novim izumom još od stvaranja interneta.
Poklonici bitkoina, od Pekinga do Buenos Ajresa, u njemu vide mogućnost postojanja finansijskog sistema bez uticaja vlade ili banaka, novu globalnu valutu digitalne ere. Digitalno zlato je neobična priča o jednom grupnom izumu, pripovest o ličnostima koje su stvorile bitkoin, uključujući i jednog finskog studenta, argentinskog milionera, kineskog preduzetnika, Tajlera i Kamerona Vinklvosa, tajanstvenog tvorca bitkoina Satošija Nakamota, kao i Rosa Ulbrihta, osnivača Silk rouda, tržišta narkotika na internetu.
„Sjajna priča. Bitkoin će preobraziti i finansijski svet i našu upotrebu interneta, a ova izuzetno zanimljiva knjiga predstavlja hroniku njegovog neverovatnog nastanka. Poperova priča se ne ispušta iz ruke, puna je živopisnih izumitelja, i predstavlja ključno štivo za svakoga ko želi da razume budućnost.“ Volter Ajzakson, autor knjige Stiv Džobs
„Bitkoin je možda tekovina informatičkih nauka, ali priča o njemu je priča o ljudima. Ovaj nadasve zabavan istorijat podseća nas da istina može biti čudnija od književnosti, i ponekad je spektar stvarnih ličnosti još neobičniji i zanimljiviji od književnih.“ Lari Samers, bivši ministar finansija SAD
-
 @ bf47c19e:c3d2573b
2025-01-22 18:55:17
@ bf47c19e:c3d2573b
2025-01-22 18:55:17Originalni tekst na dvadesetjedan.com
Autor: Vijay Boyapati / Prevod na hrvatski: Matija
Sa zadnjim cijenama koje je bitcoin dosegao 2017., optimističan scenarij za ulagače se možda čini toliko očitim da ga nije potrebno niti spominjati. Alternativno, možda se nekome čini glupo ulagati u digitalnu vrijednost koja ne počiva na nijednom fizičkom dobru ili vladi i čiji porast cijene su neki usporedili sa manijom tulipana ili dot-com balonom. Nijedno nije točno; optimističan scenarij za Bitcoin je uvjerljiv, ali ne i očit. Postoje značajni rizici kod ulaganja u Bitcoin, no, kao što planiram pokazati, postoji i ogromna prilika.
Geneza
Nikad u povijesti svijeta nije bilo moguće napraviti transfer vrijednosti među fizički udaljenim ljudima bez posrednika, poput banke ili vlade. 2008. godine, anonimni Satoshi Nakamoto je objavio 8 stranica rješenja na dugo nerješivi računalski problem poznat kao “Problem Bizantskog Generala.” Njegovo rješenje i sustav koji je izgradio - Bitcoin - dozvolio je, prvi put ikad, da se vrijednost prenosi brzo i daleko, bez ikakvih posrednika ili povjerenja. Implikacije kreacije Bitcoina su toliko duboke, ekonomski i računalski, da bi Nakamoto trebao biti prva osoba nominirana za Nobelovu nagradu za ekonomiju i Turingovu nagradu.
Za ulagače, važna činjenica izuma Bitcoina (mreže i protokola) je stvaranje novog oskudnog digitalnog dobra - bitcoina (monetarne jedinice). Bitcoini su prenosivi digitalni “novčići” (tokeni), proizvedeni na Bitcoin mreži kroz proces nazvan “rudarenje” (mining). Rudarenje Bitcoina je ugrubo usporedivo sa rudarenjem zlata, uz bitnu razliku da proizvodnja bitcoina prati unaprijed osmišljeni i predvidivi raspored. Samo 21 milijun bitcoina će ikad postojati, i većina (2017., kada je ovaj tekst napisan) su već izrudareni. Svake četiri godine, količina rudarenih bitcoina se prepolovi. Produkcija novih bitcoina će potpuno prestati 2140. godine.
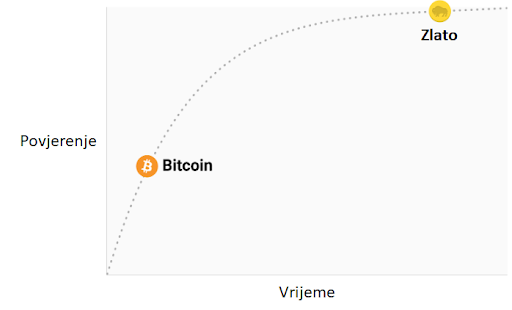 Stopa inflacije —— Monetarna baza
Stopa inflacije —— Monetarna bazaBitcoine ne podržava nikakva roba ili dobra, niti ih garantira ikakva vlada ili firma, što postavlja očito pitanje za svakog novog bitcoin ulagača: zašto imaju uopće ikakvu vrijednost? Za razliku od dionica, obveznica, nekretnina ili robe poput nafte i žita, bitcoine nije moguće vrednovati koristeći standardne ekonomske analize ili korisnost u proizvodnji drugih dobara. Bitcoini pripadaju sasvim drugoj kategoriji dobara - monetarnih dobara, čija se vrijednost definira kroz tzv. teoriju igara; svaki sudionik na tržištu vrednuje neko dobro, onoliko koliko procjenjuje da će ga drugi sudionici vrednovati. Kako bismo bolje razumjeli ovo svojstvo monetarnih dobara, trebamo istražiti podrijetlo novca.
Podrijetlo novca
U prvim ljudskim društvima, trgovina među grupama se vršila kroz robnu razmjenu. Velika neefikasnost prisutna u robnoj razmjeni je drastično ograničavala količinu i geografski prostor na kojem je bila moguća. Jedan od najvećih problema sa robnom razmjenom je problem dvostruke podudarnosti potražnje. Uzgajivač jabuka možda želi trgovati sa ribarom, ali ako ribar ne želi jabuke u istom trenutku, razmjena se neće dogoditi. Kroz vrijeme, ljudi su razvili želju za čuvanjem određenih predmeta zbog njihove rijetkosti i simbolične vrijednosti (npr. školjke, životinjski zube, kremen). Zaista, kako i Nick Szabo govori u svojem izvrsnom eseju o podrijetlu novca, ljudska želja za sakupljanjem predmeta pružila je izraženu evolucijsku prednost ranom čovjeku nad njegovim najbližim biološkim rivalom, neandertalcem - Homo neanderthalensis.
"Primarna i najbitnija evolucijska funkcija sakupljanja bila je osigurati medij za čuvanje i prenošenje vrijednosti".
Predmeti koje su ljudi sakupljali služili su kao svojevrsni “proto-novac,” tako što su omogućavale trgovinu među antagonističkim plemenima i dozvoljavale bogatsvu da se prenosi na sljedeću generaciju. Trgovina i transfer takvih predmeta bile su rijetke u paleolitskim društvima, te su oni služili više kao “spremište vrijednosti” (store of value) nego kao “medij razmjene” (medium of exchange), što je uloga koju danas igra moderni novac. Szabo objašnjava:
"U usporedbi sa modernim novcem, primitivan novac je imao jako malo “brzinu” - mogao je promijeniti ruke samo nekoliko puta u životu prosječnog čovjeka. Svejedno, trajni i čvrsti sakupljački predmet, što bismo danas nazvali “nasljeđe,” mogao je opstati mnogo generacija, dodajući znatnu vrijednost pri svakom transferu - i zapravo omogućiti transfer uopće".
Rani čovjek suočio se sa bitnom dilemom u teoriji igara, kada je odlučivao koje predmete sakupljati: koje od njih će drugi ljudi željeti? Onaj koji bi to točno predvidio imao bi ogromnu prednost u mogućnosti trgovine i akvizicije bogatsva. Neka američka indijanska plemena, npr. Naraganseti, specijalizirala su se u proizvodnji sakupljačkih dobara koja nisu imala drugu svrhu osim trgovine. Valja spomenuti da što je ranije predviđanje da će neko dobro imati takvu vrijednost, veća je prednost koju će imati onaj koji je posjeduje, zato što ju je moguće nabaviti jeftinije, prije nego postane vrlo tražena roba i njezona vrijednost naraste zajedno sa populacijom. Nadalje, nabava nekog dobra u nadi da će u budućnosti biti korišteno kao spremište vrijednosti, ubrzava upravo tu primjenu. Ova cirkularnost je zapravo povratna veza (feedback loop) koja potiče društva da se rapidno slože oko jednog spremišta vrijednosti. U terminima teorije igara, ovo je znano kao “Nashov ekvilibrij.” Postizanje Nashovog ekvilibrija za neko spremište vrijednosti je veliko postignuće za društvo, pošto ono znatno olakšava trgovinu i podjelu rada, i time omogućava napredak civilizacije.
Tisućljećima, kako su ljudska društva rasla i otvarala trgovinske puteve, različite aplikacije spremišta vrijednosti u individualnim društvima počele su se natjecati međusobno. Trgovci su imali izbor: čuvati svoju zaradu u spremištu vrijednosti vlastite kulture, ili one kulture sa kojom su trgovali, ili mješavini oboje. Benefit štednje u stranom spremištu vrijednosti bila je uvećana sposobnost trgovanja u povezanom stranom društvu. Trgovci koji su štedili u stranom spremištu vrijednosti su također imali dobrih razloga da potiču svoje društvo da ga prihvati, jer bi tako uvećali vrijednost vlastite ušteđevine. Prednosti “uvezene” tehnologije spremanja vrijednosti bile su prisutne ne samo za trgovce, nego i za sama društva. Kada bi se dvije grupe konvergirale u jedinstvenom spremištu vrijednosti, to bi značajno smanjilo cijenu troškova trgovine jednog s drugim, i samim time povećanje bogatstva kroz trgovinu. I zaista, 19. stoljeće bilo je prvi put da je najveći dio svijeta prihvatio jedinstveno spremište vrijednosti - zlato - i u tom periodu vidio najveću eksploziju trgovine u povijesti svijeta. O ovom mirnom periodu, pisao je John Maynard Keynes:
"Kakva nevjerojatna epizoda u ekonomskom napretku čovjeka… za svakog čovjeka iole iznadprosječnog, iz srednje ili više klase, život je nudio obilje, ugodu i mogućnosti, po niskoj cijeni i bez puno problema, više nego monarsima iz prethodnih perioda. Stanovnik Londona mogao je, ispijajući jutarnji čaj iz kreveta, telefonski naručiti razne proizvode iz cijele Zemlje, u količinama koje je želio, i sa dobrim razlogom očekivati njihovu dostavu na svoj kućni prag."
Svojstva dobrog spremišta vrijednosti
Kada se spremišta vrijednosti natječu jedno s drugim, specifična svojstva rade razliku koja daje jednom prednost nad drugim. Premda su mnoga dobra u prošlosti korištena kao spremišta vrijednosti ili kao “proto-novac,” određena svojstva su se pokazala kao posebno važna, i omogućila dobrima sa njima da pobijede. Idealno spremište vrijednosti biti će:
- Trajno: dobro ne smije biti kvarljivo ili lako uništeno. Tako naprimjer, žito nije idealno spremište vrijednosti.
- Prenosivo: dobro mora biti lako transportirati i čuvati, što omogućuje osiguranje protiv gubitka ili krađe i dopušta trgovinu na velike udaljenosti. Tako, krava je lošije spremište vrijednosti od zlatne narukvice.
- Zamjenjivo: jedna jedinica dobra treba biti zamjenjiva sa drugom. Bez zamjenjivosti, problem podudarnosti želja ostaje nerješiv. Time, zlato je bolje od dijamanata, jer su oni nepravilni u obliku i kvaliteti.
- Provjerljivo: dobro mora biti lako i brzo identificirano i testirano za autentičnost. Laka provjera povećava povjerenje u trgovini i vjerojatnost da će razmjena biti dovršena.
- Djeljivo: dobro mora biti lako djeljivo na manje dijelove. Premda je ovo svojstvo bilo manje važno u ranim društvima gdje je trgovina bila rijetka, postalo je važnije sa procvatom trgovine. Količine koje su se mijenjale postale su manje i preciznije.
- Oskudno: Monetarno dobro mora imati “cijenu nemoguću za lažirati,” kao što je rekao Nick Szabo. Drugim riječima, dobro ne smije biti obilno ili lako dostupno kroz proizvodnju. Oskudnost je možda i najvažnije svojstvo spremišta vrijednosti, pošto se izravno vezuje na ljudsku želju da sakupljamo ono što je rijetko. Ona je izvor vrijednosti u spremištu vrijednosti.
- Duge povijesti: što je dulje neko dobro vrijedno za društvo, veća je vjerojatnost da će biti prihvaćeno kao spremište vrijednosti. Dugo postojeće spremište vrijednosti biti će jako teško uklonjeno od strane došljaka, osim u slučaju sile (ratno osvajanje) ili ako je nova tehnologija znatno bolja u ostalim svojstvima.
- Otporno na cenzuru: novije svojstvo, sve više važno u modernom digitalnom svijetu sa sveprisutnim nadzorom, je otpornost na cenzuru. Drugim riječima, koliko je teško da vanjski agent, kao korporacija ili država, spriječi vlasnika dobra da ga čuva i koristi. Dobra koja su otporna na cenzuru su idealna za ljude koji žive u režimima koji prisilno nadziru kapital ili čine neke oblike mirne trgovine protuzakonitima.
Ova tablica ocjenjuje Bitcoin, zlato (gold) i fiat novac (kao što je euro ili dolar) po svojstvima izlistanim gore. Objašnjenje svake ocjene slijedi nakon tablice.
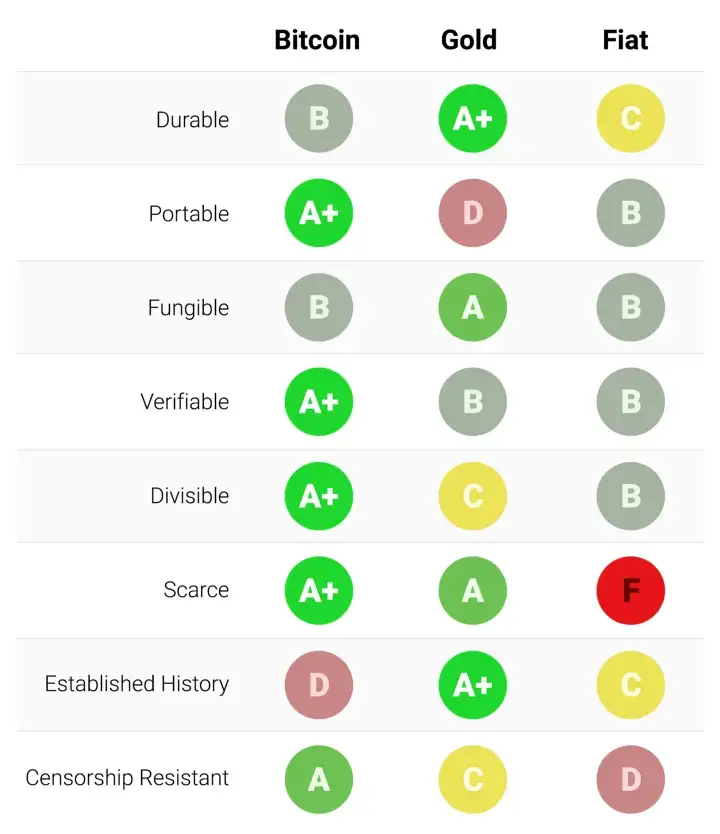
Trajnost:
Zlato je neosporeni kralj trajnosti. Velika većina zlata pronađenog kroz povijest, uključujući ono egipatskih faraona, opstaje i danas i vjerojatno će postojati i za tisuću godina. Zlatnici korišteni u antičko doba imaju značajnu vrijednost i danas. Fiat valute i bitcoini su digitalni zapisi koji ponekad imaju fizički oblik (npr. novčanice). Dakle, njihovu trajnost ne određuju njihova fizička svojstva (moguće je zamijeniti staru i oštećenu novčanicu za novu), nego institucije koje stoje iza njih. U slučaju fiat valuta, mnoge države su nastale i nestale kroz stoljeća, i valute su nestale s njima. Marke iz Weimarske republike danas nemaju vrijednost zato što institucija koja ih je izdavala više ne postoji. Ako je povijest ikakav pokazatelj, ne bi bilo mudro smatrati fiat valute trajnima dugoročno; američki dolar i britanska funta su relativne anomalije u ovom pogledu. Bitcoini, zato što nemaju instituciju koja ih održava, mogu se smatrati trajnima dok god mreža koja ih osigurava postoji. Obzirom da je Bitcoin još uvijek mlada valuta, prerano je za čvrste zaključke o njegovoj trajnosti. No, postoje ohrabrujući znakovi - prominente države su ga pokušavale regulirati, hakeri ga napadali - usprkos tome, mreža nastavlja funkcionirati, pokazujući visok stupanj antifragilnosti.
Prenosivost:
Bitcoini su najprenosivije spremište vrijednosti ikad. Privatni ključevi koji predstavljaju stotine milijuna dolara mogu se spremiti na USB drive i lako ponijeti bilo gdje. Nadalje, jednako velike sume mogu se poslati na drugi kraj svijeta skoro instantno. Fiat valute, zbog svojeg temeljno digitalnog oblika, su također lako prenosive. Ali, regulacije i kontrola kapitala od strane države mogu ugroziti velike prijenose vrijednosti, ili ih usporiti danima. Gotovina se može koristiti kako bi se izbjegle kontrole kapitala, ali onda rastu rizik čuvanja i cijena transporta. Zlato, zbog svojeg fizičkog oblika i velike gustoće, je najmanje prenosivo. Nije čudo da većina zlatnika i poluga nikad ne napuste sefove. Kada se radi prijenos zlata između prodavača i kupca, uglavnom se prenosi samo ugovor o vlasništvu, ne samo fizičko zlato. Prijenos fizičkog zlata na velike udaljenosti je skupo, riskantno i sporo.
Zamjenjivost:
Zlato nam daje standard za zamjenjivost. Kada je rastopljeno, gram zlata je praktički nemoguće razlikovati od bilo kojeg drugog grama, i zlato je oduvijek bilo takvo. S druge strane, fiat valute, su zamjenjive samo onoliko koliko njihova institucija želi da budu. Iako je uglavnom slučaj da je novčanica zamjenjiva za drugu istog iznosa, postoje situacije u kojima su velike novčanice tretirane drukčije od malih. Naprimjer, vlada Indije je, u pokušaju da uništi neoporezivo sivo tržište, potpuno oduzela vrijednost novčanicama od 500 i 1000 rupija. To je uzrokovalo da ljudi manje vrednuju te novčanice u trgovini, što je značilo da više nisu bile zaista zamjenjive za manje novčanice. Bitcoini su zamjenjivi na razini mreže; svaki bitcoin je pri prijenosu tretiran kao svaki drugi. No, zato što je moguće pratiti individualne bitcoine na blockchainu, određeni bitcoin može, u teoriji, postati “prljav” zbog korštenja u ilegalnoj trgovini, te ga trgovci ili mjenjačnice možda neće htjeti prihvatiti. Bez dodatnih poboljšanja oko privatnosti i anonimnosti na razini mrežnog protokola, bitcoine ne možemo smatrati jednako zamjenjivim kao zlato.
Mogućnost provjere:
Praktično gledajući, autentičnost fiat valuta i zlata je prilično lako provjeriti. Svejedno, i usprkos pokušajima da spriječe krivotvorenje novčanica, i dalje postoji potencijal prevare za vlade i njihove građane. Zlato također nije imuno na krivotvorenje. Sofisticirani kriminalci su koristili pozlaćeni tungsten kako bi prevarili kupce zlata. Bitcoine je moguće provjeriti sa matematičkom sigurnošću. Korištenjem kriptografskih potpisa, vlasnik bitcoina može javno demonstrirati da posjeduje bitcoine koje tvrdi da posjeduje.
Djeljivost:
Bitcoine je moguće podijeliti u stotinu milijuna manjih jedinica (zvanih satoshi), i prenositi takve (no, valja uzeti u obzir ekonomičnost prijenosa malih iznosa, zbog cijene osiguravanja mreže - “network fee”). Fiat valute su tipično dovoljno djeljive na jedinice sa vrlo niskom kupovnom moći. Zlato, iako fizički i teoretski djeljivo, postaje teško za korištenje kada se podijeli na dovoljno male količine da bi se moglo koristiti u svakodnevnoj trgovini.
Oskudnost:
Svojstvo koje najjasnije razlikuje Bitcoin od fiat valuta i zlata je njegova unaprijed definirana oskudnost. Od početka, konačna količina bitcoina nikad neće biti veća od 21 milijun. To daje vlasnicima bitcoina jasan i znan uvid u postotak ukupnog vlasništva. Naprimjer, vlasnik 10 bitcoina bi znao da najviše 2,1 milijuna ljudi (manje od 0.03% populacije) može ikad imati isto bitcoina kao i on. Premda je kroz povijest uvijek bilo oskudno, zlato nije imuno na povećanje ukupne količine. Ako se ikad izumi nova, ekonomičnija metoda rudarenja ili proizvodnje zlata, ukupna količina zlata bi se mogla dramatično povećati (npr. rudarenje morskog dna ili asteroida). Na kraju, fiat valute, relativno nov izum u povijesti, pokazale su se sklonima konstantnim povećanjima u količini. Države su pokazale stalnu sklonost inflaciji monetarne kvantitete kako bi rješavale kratkoročne političke probleme. Inflacijske tendencije vlada diljem svijeta čine fiat valute gotovo sigurnim da će gubiti vrijednost kroz vrijeme.
Etablirana povijest:
Nijedno monetarno dobro nema povijest kao zlato, koje je imalo vrijednost za cijelog trajanja ljudske civilizacije. Kovanice izrađene u antičko doba i danas imaju značajnu vrijednost. Ne može se isto reći za fiat valute, koje su same relativno nova povijesna anomalija. Od njihovog početka, fiat valute su imale gotovo univerzalni smjer prema bezvrijednosti. Korištenje inflacije kao podmuklog načina za nevidljivo oporezivanje građana je vječita kušnja kojoj se skoro nijedna država u povijesti nije mogla oduprijeti. Ako je 20. stoljeće, u kojem je fiat novac dominirao globalni monetarni poredak, demonstriralo neku ekonomsku istinu, to je onda bila ta da ne možemo računati na fiat novac da održi vrijednost u dužem ili srednjem vremenskom periodu. Bitcoin, usprkos svojoj novosti, je preživio dovoljno testova tržišta da postoji velika vjerojatnost da neće nestati kao vrijedno dobro. Nadalje, Lindy efekt govori da što duže Bitcoin bude korišten, to će veća biti vjera u njega i njegovu sposobnost da nastavi postojati dugo u budućnost. Drugim riječima, društvena vjera u monetarno dobro je asimptotička, kao u grafu ispod:
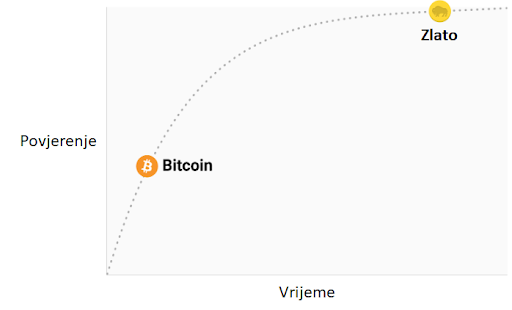
Ako Bitcoin preživi prvih 20 godina, imat će gotovo sveopće povjerenje da će trajati zauvijek, kao što ljudi vjeruju da je internet trajna stvar u modernom svijetu.
Otpor na cenzuru
Jedan od najbitnijih izvora za ranu potražnju bitcoina bila je njegova upotreba u ilegalnoj kupovini i prodaji droge. Mnogi su zato pogrešno zaključili da je primarna potražnja za bitcoinima utemeljena u njihovoj prividnoj anonimnosti. Međutim, Bitcoin nije anonimna valuta; svaka transakcija na mreži je zauvijek zapisana na javnom blockchainu. Povijesni zapis transakcija dozvoljava forenzičkoj analizi da identificira izvore i tijek sredstava. Takva analiza dovela je do uhićenja počinitelja zloglasne MtGox pljačke. Premda je istina da dovoljno oprezna i pedantna osoba može sakriti svoj identitet koristeći Bitcoin, to nije razlog zašto je Bitcoin bio toliko popularan u trgovini drogom.
Ključno svojstvo koje čini Bitcoin najboljim za takve aktivnosti je njegova agnostičnost i nepotrebnost za dozvolom (“premissionlessness”) na mrežnoj razini. Kada se bitcoini prenose na Bitcoin mreži, ne postoji nitko tko dopušta transakcije. Bitcoin je distribuirana peer-to-peer (korisnik-korisniku) mreža, i samim time dizajnirana da bude otporna na cenzuru. Ovo je u velikom kontrastu sa fiat bankarskim sustavom, u kojem države reguliraju banke i ostale institucije prijenosa novca, kako bi one prijavljivale i sprječavale protuzakonito korištenje monetarnih dobara. Klasičan primjer regulacije novca su kontrole kapitala. Npr., bogati milijunaš će vrlo teško prenijeti svoje bogatstvo u novu zemlju, kada bježi iz opresivnog režima. Premda zlato nije izdano i proizvedeno od države, njegova fizička priroda ga čini teško prenosivim kroz prostor, i samim time ga je daleko lakše regulirati nego Bitcoin. Indijski Akt kontrole zlata je primjer takve regulacije.
Bitcoin je odličan u većini gore navedenih svojstava, što mu omogućava da bude marginalno bolji od modernih i drevnih monetarnih dobara, te da pruži poticaje za svoje rastuće društveno usvajanje. Specifično, moćna kombinacija otpornosti na cenzuru i apsolutne oskudnosti bila je velika motivacija za bogate ulagače koji su uložili dio svojeg bogatstva u Bitcoin.
Evolucija novca
U modernoj monetarnoj ekonomiji postoji opsesija sa ulogom novca kao medija razmjene. U 20. stoljeću, države su monopolizirale izdavanje i kontrolu novca i kontinuirano potkopavale njegovo svojstvo spremišta vrijednosti, stvarajući lažno uvjerenje da je primarna svrha novca biti medij razmjene. Mnogi su kritizirali Bitcoin, govoreći da je neprikladan da bude novac zato što mu je cijena bila previše volatilna za medij razmjene. No, novac je uvijek evoluirao kroz etape; uloga spremišta vrijednosti je dolazila prije medija razmjene. Jedan od očeva marginalističke ekonomije, William Stanley Jevons, objašnjava:
"Povijesno govoreći… čini se da je zlato prvo služilo kao luksuzni metal za ukras; drugo, kao sačuvana vrijednost; treće, kao medij razmjene; i konačno, kao mjerilo vrijednosti."
U modernoj terminologiji, novac uvijek evoluira kroz četiri stadija:
- Kolekcionarstvo: U prvoj fazi svoje evolucije, novac je tražen samo zbog svojih posebnih svojstava, uglavnom zbog želja onog koji ga posjeduje. Školjke, perlice i zlato su bili sakupljani prije nego su poprimili poznatije uloge novca.
- Spremište vrijednosti: Jednom kada je novac tražen od dovoljnog broja ljudi, biti će prepoznat kao način za čuvanje i spremanje vrijednosti kroz vrijeme. Kada neko dobro postane široko korišteno kao spremište vrijednosti, njegova kupovna moć raste sa povećanom potražnjom za tu svrhu. Kupovna moć spremišta vrijednosti će u jednom trenutku doći do vrhunca, kada je dovolno rašireno i broj novih ljudi koji ga potražuju splasne.
- Sredstvo razmjene: Kada je novac potpuno etabliran kao spremište vrijednosti, njegova kupovna moć se stabilizira. Nakon toga, postane prikladno sredstvo razmjene zbog stabilnosti svoje cijene. U najranijim danima Bitcoina, mnogi ljudi nisu shvaćali koju buduću cijenu plaćaju koristeći bitcoine kao sredstvo razmjene, umjesto kao novonastalo spremište vrijednosti. Poznata priča o čovjeku koji je za 10,000 bitcoina (vrijednih oko 94 milijuna dolara kada je ovaj članak napisan) za dvije pizze ilustrira ovaj problem.
- Jedinica računanja vrijednosti: Jednom kada je novac široko korišten kao sredstvo razmjene, dobra će biti vrednovana u njemu, tj. većina cijena će biti izražena u njemu. Uobičajena zabluda je da je većinu dobara moguće zamijeniti za bitcoine danas. Npr., premda je možda moguće kupiti šalicu kave za bitcoine, izlistana cijena nije prava bitcoin cijena; zapravo se radi o cijeni u državnoj valuti koju želi trgovac, preračunatu u bitcoin po trenutnoj tržišnoj cijeni. Kad bi cijena bitcoina pala u odnosu na valutu, vrijednost šalice izražena u bitcoinima bi se povećala. Od trenutka kada trgovci budu voljni prihvaćani bitcoine kao platežno sredstvo, bez obraćanja pažnje na vrijednost bitcoina u državnoj fiat valuti, moći ćemo reći da je Bitcoin zaista postao jedinica računanja vrijednosti.
Monetarna dobra koja još nisu jedinice računanja vrijednosti možemo smatrati “djelomično monetiziranima.” Danas zlato ima takvu ulogu, jer je spremište vrijednosti, ali su mu uloge sredstva razmjene i računanja vrijednosti oduzete intervencijama država. Moguće je također da se jedno dobro koristi kao sredstvo razmjene, dok druga ispunjavaju ostale uloge. To je tipično u zemljama gdje je država disfunkcionalna, npr. Argentina ili Zimbabwe. U svojoj knjizi, Digitalno zlato, Nathaniel Popper piše:
"U Americi, dolar služi trima funkcijama novca: nudi sredstvo razmjene, jedinicu za mjerenje vrijednosti dobara, i mjesto gdje se može čuvati vrijednosti. S druge strane, argentinski peso je korišten kao sredstvo razmjene (za svakodnevne potrebe), ali ga nitko nije koristio kao spremište vrijednosti. Štednja u pesosima bila je ekvivalent bacanja novca. Zato su ljudi svu svoju štednju imali u dolarima, jer je dolar bolje čuvao vrijednost. Zbog volatilnosti pesosa, ljudi su računali cijene u dolarima, što im je pružalo pouzdaniju jedinicu mjerenja kroz vrijeme."
Bitcoin je trenutno u fazi tranzicije iz prvog stadija monetizacije u drugi. Vjerojatno će proći nekoliko godina prije nego Bitcoin pređe iz začetaka spremišta vrijednosti u istinski medij razmjene, i put do tog trenutka je još uvijek pun rizika i nesigurnosti. Važno je napomenuti da je ista tranzicija trajala mnogo stoljeća za zlato. Nitko danas živ nije doživio monetizaciju dobra u realnom vremenu (kroz koju Bitcoin prolazi), tako da nemamo puno iskustva govoriti o putu i načinu na koji će se monetizacija dogoditi.
Put monetizacije
Kroz proces monetizacije, monetarno dobro će naglo porasti u kupovnoj moći. Mnogi su tako komentirali da je uvećanje kupovne moći Bitcoina izgledalo kao “balon” (bubble). Premda je ovaj termin često korišten kako bi ukazao na pretjeranu vrijednosti Bitcoina, sasvim slučajno je prikladan. Svojstvo koje je uobičajeno za sva monetarna dobra jest da je njihova kupovna moć viša nego što se može opravdati samo kroz njihovu uporabnu vrijednost. Zaista, mnogi povijesni novci nisu imali uporabnu vrijednost. Razliku između kupovne moći i vrijednosti razmjene koju bi novac mogao imati za svoju inherentnu korisnost, možemo razmatrati kao “monetarnu premiju.” Kako monetarno dobro prolazi kroz stadije monetizacije (navedene gore), monetarna premija raste. No, ta premija ne raste u ravnoj i predvidivoj liniji. Dobro X, koje je bilo u procesu monetizacije, može izgubiti u usporedbi sa dobrom Y koje ima više svojstava novca, te monetarna premija dobra X drastično padne ili potpuno nestane. Monetarna premija srebra je skoro potpuno nestala u kasnom 19. stoljeću, kada su ga vlade diljem svijeta zamijenile zlatom kao novcem.
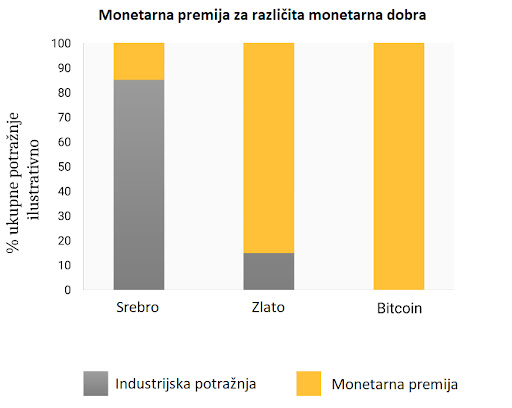
Čak i u odsustvu vanjskih faktora, kao što su intervencije vlade ili druga monetarna dobra, monetarna premija novog novca neće ići predvidivim putem. Ekonomist Larry White primijetio je:
"problem sa pričom “balona,” naravno, je da je ona konzistentna sa svakim putem cijene, i time ne daje ikakvo objašnjenje za specifičan put cijene"
Proces monetizacije opisuje teorija igara; svaki akter na tržištu pokušava predvidjeti agregiranu potražnju ostalih aktera, i time buduću monetarnu premiju. Zato što je monetarna premija nevezana za inherentnu korisnost, tržišni akteri se uglavnom vode za prošlim cijenama da bi odredili je li neko dobro jeftino ili skupo, i žele li ga kupiti ili prodati. Veza trenutne potražnje sa prošlim cijenama naziva se “ovisnost o putu” (path dependence); ona je možda najveći izvor konfuzije u shvaćanju kretanja cijena monetarnih dobara.
Kada kupovna moć monetarnog dobra naraste zbog većeg i šireg korištenja, očekivanja tržišta o definicijama “jeftinog” i “skupog” se mijenjaju u skladu s time. Slično tome, kada cijena monetarnog dobra padne, očekivanja tržišta mogu se promijeniti u opće vjerovanje da su prethodne cijene bile “iracionalne” ili prenapuhane. Ovisnost o putu novca ilustrirana je riječima poznatog upravitelja fondova s Wall Streeta, Josha Browna:
"Kupio sam bitcoine kada su koštali $2300, i to mi se udvostručilo gotovo odmah. Onda sam počeo govoriti kako “ne mogu kupiti još” dok im je cijena rasla, premda sam znao da je to razmišljanje bazirano samo na cijenu po kojoj sam ih kupio. Kasnije, kada je cijena pala zbog kineske regulacije mjenjačnica, počeo sam si govoriti, “Odlično, nadam se da će još pasti da mogu kupiti još.”"
Istina leži u tome da su ideje “jeftinog” i “skupog” zapravo besmislene kada govorimo o monetarnim dobrima. Cijena monetarnog dobra ne reflektira njegovu stopu rasprostanjenosti ili korisnosti, nego mjeru koliko je ono široko prihvaćeno da ispuni razne uloge novca.
Dodatna komplikacija u ovom aspektu novca je činjenica da tržišni akteri ne djeluju samo kao nepristrani promatrači koji pokušavaju kupiti i prodati u iščekivanju budućih kretanja monetarne premije, nego i kao aktivni proponenti. Pošto ne postoji objektivno “točna” monetarna premija, širiti dobar glas o superiornijim svojstvima nekog monetarnog dobra je efektivnije nego za obična dobra, čija vrijednost je u konačnici vezana na njegovu osnovnu korisnost. Religiozni zanos sudionika na Bitcoin tržištu vidljiv je na raznim internetskim forumima, gdje Bitcoineri aktivno promoviraju benefine Bitcoina i bogatstvo koje je moguće ostvariti investiranjem u njega. Promatrajući Bitcoin tržište, Leigh Drogen komentira:
"To je prepoznatljivo svima kao religija - priča koju si pričamo i oko koje se slažemo. Religija je krivulja na grafu prihvaćanja o kojoj trebamo razmišljati. Sustav je gotovo savršen - onog trenutka kada netko pristupi krugu Bitcoinera, to će reći svima i nastaviti širiti riječ. Onda njihovi prijatelji pristupe i nastave širiti riječ."
Premda usporedba sa religijom može staviti Bitcoin u iracionalno svjetlo, potpuno je racionalno za individualnog vlasnika da širi dobru vijest o superiornom monetarnom dobru, i za šire društvo da se standardizira oko njega. Novac djeluje kao temelj za svu trgovinu i štednju; tako da prihvaćanje superiornog oblika novca ima ogromne multiplicirajuće benefite za stvaranje bogatstva za sve članove društva.
Oblik monetizacije
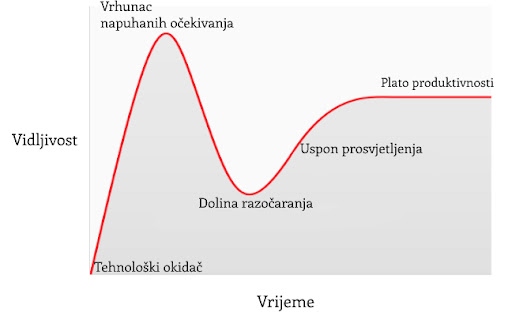
U članku o Spekulativnom prihvaćanju Bitcoina / teorije cijene, Michael Casey postulira da rastući Gartner hype ciklusi predstavljaju faze standardne S-krivulje prihvaćanja novih tehnologija, koje su bile prisutne kod mnogih transformacijskih tehnologija dok su postajale uobičajene u društvu.
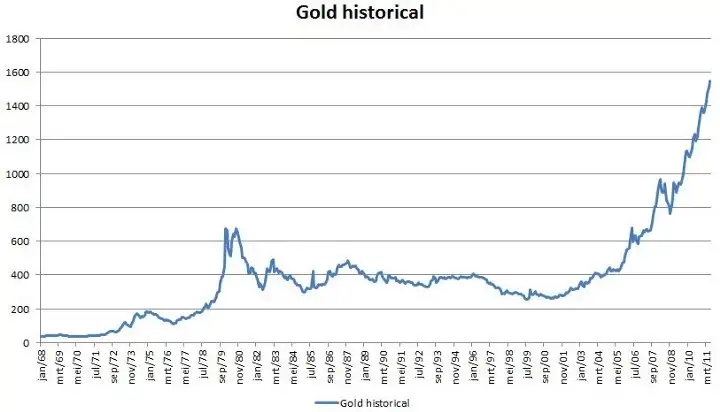
Svaki Gartner hype ciklus počinje sa eksplozijom entuzijazma za novom tehnologijom, a cijenu podižu oni sudionici na tržištvu koji su “dostupni” u toj fazi. Najraniji kupci u Gartner hype ciklusu obično imaju jaku vjeru o transformacijskoj prirodi tehnologije u koju ulažu. S vremenom, tržište dosegne vrhunac entuzijazma kako se količina novih kupaca iscrpljuje, te kupovinom počnu dominirati spekulatori koji su više zainteresirani u brze profite nego u samu tehnologiju.
Nakon vrha hype ciklusa, cijene rapidno padaju dok spekulativno ludilo ustupa mjesto očajavanju, javnoj poruzi i osjećaju da tehnologija nije uopće bila transformacijska. S vremenom, cijena dosegne dno i formira plato na kojem se originalnim ulagačima, koji su imali snažno uvjerenje, pridružuju nove grupe ljudi koji su izdržali bol kraha cijena i koji cijene važnost same tehnologije.
Plato traje neko vrijeme i formira, kako Casey kaže, “stabilnu, dosadnu dolinu.” Za ovo vrijeme, javni interes za tehnologiju opada, no nastaviti će se razvijati i snažna zajednica uvjerenja će polako rasti. Tada, postavlja se nova baza za sljedeću iteraciju hype ciklusa, dok vanjski promatrači prepoznaju da tehnologija i dalje postoji i da ulaganje u nju možda nije onoliko rizično kao što se činilo za vrijeme pada cijene. Sljedeća iteracija hype ciklusa donosi mnogo veći broj novih ljudi, pa je i ciklus daleko veći u svojoj magnitudi.
Jako mali broj ljudi koji sudjeluju u Gartner hype ciklusu će točno predvidjeti koliko će visoko cijena porasti za vrijeme ciklusa. Cijene često dosegnu razine koje bi se činile apsurdnima većini ulagača u raniji stadijima ciklusa. Kada ciklus završi, mediji tipično atribuiraju pad cijene nekoj od aktualnih drušvenih tema. Premda takva tema može biti okidač pada, ona nikad nije temeljni razlog zašto ciklus završava. Gartner hype ciklusi završavaju kada je količina dostupnih novih sudionika na tržištu iscrpljena.
Zanimljivo je da je i zlato nacrtalo klasičan graf Gartner hype ciklusa od kasnih 1970-ih do ranih 2000-ih. Moguće je spekulirati da je hype ciklus osnovna socijalna dinamika oko procesa monetizacije.
Gartner kohorte
Od početka trgovanja Bitcoina na mjenjačnicama 2010. godine, Bitcoin tržište je svjedočilo četirima velikim Gartner hype ciklusima. U retrospektivi, možemo vrlo precizno identificirati grupe cijena prethodnih hype ciklusa Bitcoin tržišta. Također, možemo kvalitativno odrediti kohorte ulagača koje su povezane sa svakom iteracijom prethodnih ciklusa.
$0–$1 (2009. – 3. mjesec 2011.): Prvi hype ciklus u Bitcoin tržištu dominirali su kriptografi, računalni znanstvenici i cypherpunkovi koji su od početka bili spremni razumijeti važnost nevjerojatnog izuma Satoshija Nakamotoa, i koji su bili pioniri u potvrđivanju da Bitcoin protokol nema tehničkih mana.
$1–$30 (3. mjesec 2011. – 7. mjesec. 2011.): Drugi ciklus privukao je rane entuzijaste oko novih tehnologija kao i stabilan pritok ideološki motiviranih ulagača koji su bili oduševljeni idejom novca odvojenog od države. Libertarijanci poput Rogera Vera došli su u Bitcoin zbog aktivnog anti-institucionalnog stava, i mogućnosti koju je nova tehnologija obećavala. Wences Casares, briljantni i dobro povezani serijski poduzetnik, bio je također dio drugog Bitcoin hype ciklusa te je širio riječ o Bitcoinu među najprominentnijim tehnolozima i ulagačima u Silicijskoj Dolini.
$250–$1100 (4. mjesec 2013. – 12. mjesec 2013.): Treći hype ciklus doživio je ulazak ranih generalnih i institucionalnih ulagača koji su bili voljni uložiti trud i riskirati kroz užasno komplicirane kanale likvidnosti kako bi kupili bitcoine. Primaran izvor likvidnosti na tržištu za vrijeme ovog perioda bio je MtGox, mjenjačnica bazirana u Japanu, koju je vodio notorno nesposobni i beskrupulozni Mark Karpeles, koji je kasnije završio i u zatvoru zbog svoje uloge u kolapsu MtGoxa.
Valja primijetiti da je rast Bitcoinove cijene za vrijeme spomenuti hype ciklusa većinom povezano sa povećanjem likvidnosti i lakoćom sa kojom su ulagači mogli kupiti bitcoine. Za vrijeme prvog hype ciklusa, nisu postojale mjenjačnice; akvizicija bitcoina se odvijala primarno kroz rudarenje (mining) ili kroz izravnu razmjenu sa onima koju su već izrudarili bitcoine. Za vrijeme drugog hype ciklusa, pojavile su se rudimentarne mjenjačnice, no nabavljanje i osiguravanje bitcoina na ovim mjenjačnicama bilo je previše kompleksno za sve osim tehnološki najsposobnijih ulagača. Čak i za vrijeme trećeg hype ciklusa, ulagači koju su slali novac na MtGox kako bi kupili bitcoine su morali raditi kroz značajne prepreke. Banke nisu bile voljne imati posla sa mjenjačnicom, a oni posrednici koji su nudili usluge transfera bili su često nesposobni, kriminalni, ili oboje. Nadalje, mnogi koji su uspjeli poslati novac MtGoxu, u konačnici su morali prihvatiti gubitak svojih sredstava kada je mjenjačnica hakirana i kasnije zatvorena.
Tek nakon kolapsa MtGox mjenjačnice i dvogodišnje pauze u tržišnoj cijeni Bitcoina, razvili su se zreli i duboki izvori likvidnosti; primjeri poput reguliranih mjenjačnica kao što su GDAX i OTC brokeri kao Cumberland mining. Dok je četvrti hype ciklus započeo 2016. godine, bilo je relativno lako običnim ulagačima kupiti i osigurati bitcoine.
$1100–$19600? (2014. –?):
U trenutku pisanja ovog teksta, tržište Bitcoina je prolazilo svoj četvrti veliki hype ciklus. Sudjelovanje u ovom hype ciklusu dominirala je ona skupina koju je Michael Casey opisao kao “rana većina” običnih i institucionalnih ulagača.
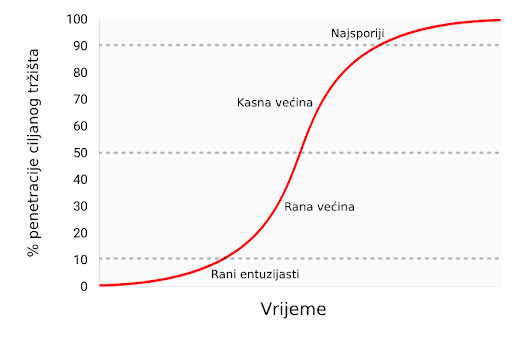
Kako su se izvori likvidnosti produbljivali i sazrijevali, veliki institucionalni ulagači sada imaju priliku sudjelovati kroz regulirana “futures” tržišta. Dostupnosti takvih tržišta stvara put ka kreaciji Bitcoin ETF-a (exchange traded fund) (fond na slobodnom tržištu), koji će onda pokrenuti “kasnu većinu” i “najsporije” u sljedećim hype ciklusima.
Premda je nemoguće predvidjeti točan efekt budućih hype ciklusa, razumno je očekivati da će najviša točka biti između $20,000 i $50,000 (2021. zenit je bio preko $69,000). Znatno više od ovog raspona, i Bitcoin bi imao znatan postotak ukupne vijednosti zlata (zlato i Bitcoin bi imali jednaku tržišnu kapitalizaciju kada bi bitcoini vrijedili oko $380,000 u trenutku pisanja ovog teksta). Značajan postotak vrijednosti zlata dolazi od potražnje centralnih banaka, te je malo vjerojatno da će centralne banke ili suverene države sudjelovati u trenutnom hype ciklusu.
Ulazak suverenih država u Bitcoin
Bitcoinov zadnji Gartner hype ciklus će započeti kada ga suverene države počnu akumulirati kao dio svojih rezervi stranih valuta. Tržišna kapitalizacija Bitcoina je trenutno premala da bismo ga smatrali značajnim dodatkom rezervama većini zemalja. No, kako se interes u privatnom sektoru povećava i kapitalizacija Bitcoina se približi trilijunu dolara, postat će dovoljno likvidan za većinu država. Prva država koja službeno doda bitcoine u svoje rezerve će vjerojatno potaknuti stampedo ostalih da učine isto. Države koje su među prvima u usvajanju Bitcoina imat će najviše benefita u svojim knjigama ako Bitcoin u konačnici postane globalna valuta (global reserve currency). Nažalost, vjerojatno će države sa najjačom izvršnom vlasti - diktature poput Sjeverne Koreje - biti najbrže u akumulaciji bitcoina. Neodobravanje prema takvim državama i slaba izvršna tijela zapadnjačkih demokracija uzrokovat će sporost i kašnjenje u akumulaciji bitcoina za njihove vlastite rezerve.
Velika je ironija u tome što je SAD trenutno jedna od regulatorno najotvorenijih nacija prema Bitcoinu, dok su Kina i Rusija najzatvorenije. SAD riskira najviše, geopolitički, ako bi Bitcoin zamijenio dolar kao svjetska rezervna valuta. U 1960-ima, Charles de Gaulle je kritizirao “pretjeranu privilegiju” (“exorbitant privilege”) koju su SAD imale u međunarodnom monetarnom poretku, postavljenom kroz Bretton Woods dogovor 1944. godine. Ruska i kineska vlada još ne shvaćaju geo-strateške benefite Bitcoina kao rezervne valute, te se trenutno brinu o efektima koje bi mogao imati na njihova unutarnja tržišta. Kao de Gaulle u 1960-ima, koji je prijetio SAD-u povratkom na klasični standard zlata, Kinezi i Rusi će s vremenom uvidjeti korist u velikoj poziciji u Bitcoinu - spremištu vrijednosti bez pokrića ijedne vlade. Sa najvećom koncentracijom rudara Bitcoina u Kini (2017.), kineska vlada već ima znatnu potencijalnu prednost u stavljanju bitcoina u svoje rezerve.
SAD se ponosi svojim statusom nacije inovatora, sa Silicijskom dolinom kao krunom svoje ekonomije. Dosad, Silicijska dolina je dominirala konverzacijom usmjerenom prema regulaciji, i poziciji koju bi ona treba zauzeti prema Bitcoinu. No, bankovna industrija i federalna rezerva SAD-a (US Federal Reserve, Fed) napokon počinju uviđati egzistencijalnu prijetnju koju Bitcoin predstavlja za američku monetarnu politiku, postankom globalne rezervne valute. Wall Street Journal, jedan od medijskih glasova federalne reserve, izdao je komentar o Bitcoinu kao prijetnji monetarnoj politici SAD-a:
"Postoji još jedna opasnost, možda i ozbiljnija iz perspektive centralnih banaka i regulatora: bitcoin možda ne propadne. Ako je spekulativni žar u kriptovalutu samo prvi pokazatelj njezinog šireg korištenja kao alternative dolaru, Bitcoin će svakako ugroziti monopol centralnih banaka nad novcem."
U narednim godinama, možemo očekivati veliku borbu između poduzetnika i inovatora u Silicijskoj dolini, koji će pokušavati čuvati Bitcoin od državne kontrole s jedne strane, i bankovne industrije i centralnih banaka koje će učiniti sve što mogu da bi regulirale Bitcoin kako bi spriječile znatne promjene u svojoj industriji i moći izdavanja novca, s druge.
Prijelaz na medij razmjene
Monetarno dobro ne može postati opće prihvaćen medij razmjene (standardna ekonomska definicija za “novac”) prije nego je vrednovano od širokog spektra ljudi; jednostavno, dobro koje nije vrednovano neće biti prihvaćeno u razmjeni. Kroz proces generalnog rasta vrijednosti, i time postanka spremišta vrijednosti, monetarno dobro će brzo narasti u kupovnoj moći, i time stvoriti cijenu za korištenje u razmjeni. Samo kada ta cijena rizika mijenjanja spremišta vrijednosti padne dovoljno nisko, može dobro postati opće prihvaćen medij razmjene.
Preciznije, monetarno dobro će biti prikladno kao medij razmjene samo kada je suma cijene rizika i transakcijske cijene u razmjeni manja nego u trgovini bez tog dobra.
U društvu koje vrši robnu razmjenu, prijelaz spremišta vrijednosti u medij razmjene može se dogoditi čak i onda kada monetarno dobro raste u kupovnoj moći, zato što su transakcijski troškovi robne razmjene iznimno visoki. U razvijenoj ekonomiji, u kojoj su troškovi razmjene niski, moguće je za mladu i rapidno rastućnu tehnologiju spremišta vrijednosti, poput Bitcoina, da se koristi kao medij razmjene, doduše na ograničen način. Jedan primjer je ilegalno tržište droge, gdje su kupci voljni žrtvovati oportunu cijenu čuvanja bitcoina kako bi umanjili znatan rizik kupovine droge koristeći fiat novac.
Postoje međutim velike institucionalne barijere da novonastalo spremište vrijednosti postane sveopće prihvaćen medij razmjene u razvijenom društvu. Države koriste oporezivanje kao moćnu metodu zaštite svojeg suverenog novca protiv rivalskih monetarnih dobara. Ne samo da suvereni novac ima prednost konstantnog izvora potražnje, zato što je porez moguće platiti jedino u njemu, nego su i rivalska monetarna dobra oporezana pri svakoj razmjeni za vrijeme rastuće cijene. Ova metoda oporezivanja stvara znatan otpor korištenju spremišta vrijednosti kao medija razmjene.
Ovakvo sabotiranje tržišnih monetarnih dobara nije nepremostiva barijera za njihovo prihvaćanje kao općeg medija razmjene. Ako ljudi izgube vjeru u suvereni novac, njegova vrijednost može rapidno propasti kroz proces zvan hiperinflacija. Kada suvereni novac prolazi kroz hiperinflaciju, njegova vrijednost propadne prvo u usporedbi sa najlikvidnijim dobrima u društvu, kao što je zlato ili stabilna strana valuta (američki dolar npr.), ako su ona dostupna. Kada nema likvidnih dobara ili ih ima premalo, novac u hiperinflaciji kolabira u usporedbi sa stvarnim dobrima, kao što su nekretnine ili upotrebljiva roba. Arhetipska slika hiperinflacije je trgovina sa praznim policama - potrošači brzo bježe iz propadajuće vrijednosti novca svoje nacije.

Nakon dovoljno vremena, kada je vjera potpuno uništena za vrijeme hiperinflacije, suvereni novac više nitko ne prihvaća, te se društvo može vratiti na robnu razmjenu, ili će doživjeti potpunu zamjenu monetarne jedinice za sredstvo razmjene. Primjer ovog procesa bila je zamjena zimbabveanskog dolara za američki dolar. Takva promjena suverenog novca za stranu valutu je dodatno otežana relativnom oskudnošću strane valute i odsustvom stranih bankarskih institucija koje pružaju likvidnost tržištu.
Sposobnost lakog prenošenja bitcoina preko granica i odsustvo potrebe za bankarskim sustavom čine Bitcoin idealnim monetarnim dobrom za one ljude koji pate pod hiperinflacijom. U nadolazećim godinama, kako fiat valute nastave svoj povijesni trend ka bezvrijednosti, Bitcoin će postati sve popularniji izbor za ušteđevine ljudi diljem svijeta. Kada je novac nacije napušten i zamijenjen Bitcoinom, Bitcoin će napraviti tranziciju iz spremišta vrijednosti u tom društvu u opće prihvaćeno sredstvo razmjene. Daniel Krawicz stvorio je termin “hiperbitcoinizacija” da bi opisao ovaj proces.
Učestala pogrešna shvaćanja
Većina ovog članka usredotočila se na monetarnu prirodu Bitcoina. Sa tim temeljima možemo adresirati neke od najčešćih nerazumijevanja u Bitcoinu.
Bitcoin je balon (bubble)
Bitcoin, kao sva tržišna monetarna dobra, posjeduje monetarnu premiju. Ona često rezultira uobičajenom kritikom da je Bitcoin samo “balon.” No, sva monetarna dobra imaju monetarnu premiju. Naprotiv, ta monetarna premija (cijena viša od one koju diktira potražnja za dobrom kao korisnim) je upravo karakteristična za sve oblike novca. Drugim riječima, novac je uvijek i svuda balon. Paradoksalno, monetarno dobro je istovremeno balon i ispod vrijednosti ukoliko je u ranijim stadijima općeg prihvaćanja kao novac.
Bitcoin je previše volatilan
Volatilnost cijene Bitcoina je funkcija njegovog nedavnog nastanka. U prvih nekoliko godina svojeg postojanja, Bitcoin se ponašao kao mala dionica, i svaki veliki kupac - kao npr. braća Winklevoss - mogao je uzrokovati veliki skok u njegovoj cijeni. No, kako su se prihvaćenost i likvidnost povećavali kroz godine, volatilnost Bitcoina je srazmjerno smanjila. Kada Bitcoin postigne tržišnu kapitalizaciju (vrijednost) zlata, imat će sličnu volatilnost kao i zlato. Kako Bitcoin nastavi rasti, njegova volatilnost će se smanjiti do razine koja ga čini prikladnim za široko korištenje kao medij razmjene. Kao što je prethodno rečeno, monetizacija Bitcoina se odvija u seriji Gartner hype ciklusa. Volatilnost je najniža za vrijeme vrhunaca i dolina unutar ciklusa. Svaki hype ciklus ima nižu volatilnost od prethodnih, zato što je likvidnost tržišta veća.
Cijene transakcija su previsoke
Novija kritika Bitcoin mreže je ta da ju je povećanje cijena prijenosa bitcoina učinilo neprikladnom za sustav plaćanja. No, rast u cijenama transakcija je zdrav i očekivan. One su nužne za plaćanje bitcoin minera (rudara), koji osiguravaju mrežu validacijom transakcija. Rudare se plaća kroz cijene transakcija ili kroz blok-nagrade, koje su inflacijska subvencija od trane trenutnih vlasnika bitcoina.
S obzirom na Bitcoinovu fiksnu proizvodnju (monetarna politika koja ga čini idealnim za spremanje vrijednosti), blok-nagrade će s vremenom nestati i mrežu će se u konačnici morati osiguravati kroz cijene transakcija. Mreža sa “niskim” cijenama transakcija je mreža sa slabom sigurnosti i osjetljiva na vanjsku intervenciju i cenzuru. Oni koji hvale niske cijene Bitcoinovih alternative zapravo niti ne znajući opisuju slabosti tih takozvanih “alt-coina.”
Površan temelj kritika Bitcoinovih “visokih” cijena transakcija je uvjerenje da bi Bitcoin trebao biti prvo sustav plaćanja, i drugo spremište vrijednosti. Kao što smo vidjeli kroz povijest novca, ovo uvjerenje je naopako. Samo onda kada Bitcoin postane duboko ukorijenjeno spremište novca može biti prikladan kao sredstvo razmjene. Nadalje, kada oportunitetni trošak razmjene bitcoina dođe na razinu koja ga čini prikladnim sredstvom razmjene, većina trgovine neće se odvijati na samoj Bitcoin mreži, nego na mrežama “drugog sloja” (second layer) koje će imati niže cijene transakcija. Takve mreže, poput Lightning mreže, služe kao moderna verzija zadužnica koje su korištene za prijenos vlasničkih papira zlata u 19. stoljeću. Banke su koristile zadužnice zato što je prijenos samog metala bio daleko skuplji. Za razliku od takvih zadužnica, Lightning mreža će omogućavati nisku cijenu prijenosa bitcoina bez potrebe za povjerenjem prema trećoj strani, poput banaka. Razvoj Lightning mreže je tehnološka inovacija od izuzetne važnosti u povijesti Bitcoina, i njezina vrijednost će postati očita u narednim godinama, kako je sve više ljudi bude razvijalo i koristilo.
Konkurencija
Pošto je Bitcoin softverski protokol otvorenog tipa (open-source), oduvijek je bilo moguće kopirati softver i imitirati mrežu. Kroz godine nastajali su mnogi imitatori, od identičnih kopija, kao Litecoin, do kompleksnijih varijanti kao što je Ethereum, koje obećavaju arbitrarno kompleksne ugovorne mehanizme koristeći decentralizirani računalni sustav. Česta kritika Bitcoinu od strane ulagača je ta da on ne može zadržati svoju vrijednost kada je vrlo lako stvoriti konkurente koji mogu lako i brzo u sebi imati najnovije inovacije i softverske funkcionalnosti.

Greška u ovom argumentu leži u manju takozvanog “mrežnog efekta” (network effect), koji postoji u prvoj i dominantnoj tehnologiji u nekom području. Mrežni efekt - velika vrijednost korištenja Bitcoina samo zato što je već dominantan - je važno svojstvo samo po sebi. Za svaku tehnologiju koja posjeduje mrežni efekt, to je daleko najvažnije svojstvo koje može imati.
Za Bitcoin, mrežni efekt uključuje likvidnost njegovog tržišta, broj ljudi koji ga posjeduju, i zajednicu programera koji održavaju i unaprjeđuju njegov softver i svjesnost u javnosti. Veliki ulagači, uključujući države, će uvijek prvo tražiti najlikvidnije tržište, kako bi mogli ući i izaći iz tržišta brzo, i bez utjecanja na cijenu. Programeri će se pridružiti dominantnoj programerskoj zajednici sa najboljim talentom, i time pojačati samu zajednicu. Svjesnost o brendu sama sebe pojačava, pošto se nadobudni konkurenti Bitcoina uvijek spominju u kontekstu Bitcoina kao takvog.
Raskrižje na putu (fork)
Trend koji je postao popularan 2017. godine nije bio samo imitacija Bitcoinovog softvera, nego kopiranje potpune povijesti njegovih prošlih transakcija (cijeli blockchain). Kopiranjem Bitcoinovog blockchaina do određene točke/bloka i odvajanjem sljedećih blokova ka novoj mreži, u procesu znanom kao “forking” (odvajanje), Bitcoinovi konkurenti su uspjeli riješiti problem distribuiranja svojeg tokena velikom broju korisnika.

Najznačajniji takav fork dogodio se 1. 8. 2017. godine, kada je nova mreža nazvana Bitcoin Cash (Bcash) stvorena. Vlasnik N količine bitcoina prije 1.8.2017. bi onda posjedovao N bitcoina i N BCash tokena. Mala, ali vrlo glasna zajednica Bcash proponenata je neumorno pokušavala prisvojiti Bitcoinov brend i ime, imenujući svoju novu mrežu Bitcoin Cast i pokušavajući uvjeriti nove pridošlice u Bitcoin da je Bcash “pravi” Bitcoin. Ti pokušaji su većinom propali, i taj neuspjeh se vidi u tržišnim kapitalizacijama dviju mreža. No, za nove ulagače, i dalje postoji rizik da bi konkurent mogao kopirati Bitcoin i njegov blockchain i tako uspjeti u preuzimanju tržišne kapitalizacije, te postati de facto Bitcoin.
Moguće je uočiti važno pravilo gledajući velike forkove u prošlosti Bitcoin i Ethereum mreža. Većina tržišne kapitalizacije odvijat će se na mreži koja zadrži najviši stupanj talenta i aktivnosti u zajednici programera. Premda se na Bitcoin može gledati kao na nov i mlad novac, on je također računalna mreža koja počiva na softveru, kojeg se pak treba održavati i poboljšavati. Kupovina tokena na mreži koja ima malo neiskusnih programera bilo bi kao kupovati kopiju Microsoft Windowsa na kojoj rade lošiji programeri. Jasno je vidljivo iz povijesti forkova koji su se odvili 2017. godine da su najbolji računalni i kriptografski stručnjaci posvećeni razvoju originalnog Bitcoina, a ne nekoj od rastućeg broja imitacija koje su se izrodile iz njega.
Stvarni rizici
Premda su uobičajene kritike upućene Bitconu od strane medija i ekonomske profesije krive i bazirane na netočnom shvaćanju novca, postoje pravi i značajni rizici kod ulaganja u Bitcoin. Bilo bi mudro za novog Bitcoin ulagača da shvati ove rizike prije potencijalnog ulaganja.
Rizik protokola
Bitcoin protokol i kriptografski sastavni dijelovi na kojima je sagrađen potencijalno imaju dosad nepronađenu grešku u svom dizajnu, ili mogu postati nesigurni razvojem kvantnih računala. Ako se pronađe greška u protokolu, ili neka nova metoda računarstva učini mogućim probijanje kriptografskih temelja Bitcoina, vjera u Bitcoin biti će znatno narušena. Rizik protokola bio je najviši u ranim godinama razvoja Bitcoina, kada je još uvijek bilo nejasno, čak i iskusnim kriptografima, je li Satoshi Nakamoto zaista riješio problem bizantskih generala (Byzantine Generals’ Problem). Brige oko ozbiljnih grešaka u Bitcoin protokolu nestale su kroz godine, no uzevši u obzir njegovu tehnološku prirodu, rizik protokola će uvijek ostati u Bitcoinu, makar i kao izuzetak.
Propadanje mjenjačnica
Time što je decentraliziran, Bitcoin je pokazao značajnu otpornost, suočen sa brojnim pokušajima raznih vlada da ga reguliraju ili unište. No, mjenjačnice koje trguju bitcoinima za fiat valute su centralizirani entiteti i podložne regulacijama i zatvaranju. Bez mjenjačnica i volje bankara da s njima posluju, proces monetizacije Bitcoina bio bi ozbiljno usporen, ako ne i potpuno zaustavljen. Iako postoje alternativni izvori likvidnosti za Bitcoin, poput “over-the-counter” brokera i decentraliziranih tržišta za kupovinu i prodaju bitcoina, kritičan proces otkrivanja i definiranja cijene se odvija na najlikvidnijim mjenjačnicama, koje su sve centralizirane.
Jedan od načina za umanjivanje rizika gašenja mjenjačnica je geografska arbitraža. Binance, jedna od velikih mjenjačnica iz Kine, preselila se u Japan nakon što joj je kineska vlada zabranila operiranje u Kini. Vlade su također oprezne kako ne bi ugušile novu industriju koja je potencijalno značajna kao i internet, i time predale nevjerojatnu konkurentnu vrijednost drugim nacijama.
Samo kroz koordinirano globalno ukidanje Bitcoin mjenjačnica bi proces monetizacije mogao biti zaustavljen. Trenutno smo u utrci; Bitcoin raste i postaje sve rašireniji, i doći će do trenutka kada bi potpuno ukidanje mjenjačnica postalo politički neizvedivo - kao i gašenje interneta. Mogućnost takvog ukidanja je još uvijek realna, i valja je uzeti u obzir pri ulaganju u Bitcoin. Kao što je gore objašnjeno, suverene vlade se polako bude i uviđaju prijetnju koju predstavlja neovisna digitalna valuta otporna na cenzuru, za njihovu monetarnu politiku. Otvoreno je pitanje hoće li išta poduzeti da odgovore ovoj prijetnji prije nego Bitcoin postane toliko utvrđen i raširen da politička akcija postane nemoćna i ne-efektivna.
Zamjenjivost
Otvorena i transparentna priroda Bitcoin blockchaina omogućava državama da proglase specifične bitcoine “okaljanima” zbog njihovog korištenja u određenim aktivnostima. Premda Bitcoin, na protokolarnoj razini, ne diskriminira transakcije na ikoji način, “okaljani” bitcoini bi mogli postati bezvrijedni ako bi ih regulacije proglasile ilegalnima i neprihvatljivima za mjenjačnice ili trgovce. Bitcoin bi tada izgubio jedno od kritičnih svojstava monetarnog dobra: zamjenjivost.
Da bi se ovaj problem riješio i umanjio, biti će potrebna poboljšanja na razini protokola kako bi se poboljšala privatnost transakcija. Premda postoji napredak u ovom smjeru, prvi put primjenjen u digitalnim valutama kao što su Monero i Zcash, potrebno je napraviti značajne tehnološke kompromise između efikasnosti i kompleksnosti Bitcoina i njegove privatnosti. Pitanje ostaje otvoreno je li moguće dodati nova svojstva privatnosti na Bitcoin, na način koji neće kompromitirati njegovu korisnost kao novca.
Zaključak
Bitcoin je novonastali novac koji je u procesu transformacije iz sakupljačkog dobra u spremište vrijednosti. Kao neovisno monetarno dobro, moguće je da će u budućnosti postati globalan novac, slično kao zlato za vrijeme 19. stoljeća. Prihvaćanje Bitcoina kao globalnog novca je upravo taj optimističan scenarij za Bitcoin, kojeg je artikulirao Satoshi Nakamoto još 2010. godine u email razmjeni sa Mikeom Hearnom:
"Ako zamisliš da se koristi u nekom dijelu svjetske trgovine, i da će postojati samo 21 milijun bitcoina za cijeli svijet, vrijednost po jedinici će biti znatno veća".
Ovaj scenarij je još snažnije definirao briljantni kriptograf Hal Finney, koji je ujedno primio i prve bitcoine od Nakamotoa, ubrzo nakon najave prvog funkcionalnog Bitcoin softvera:
"Zamislimo da Bitcoin bude uspješan i postane dominantan sustav plaćanja diljem svijeta. U tom slučaju će ukupna vrijednost valute biti jednaka ukupnoj vrijednosti svog bogatstva svijeta. Današnje procjene ukupnog svjetskog bogatska kućanstava koje sam pronašao borave negdje između 100 i 300 trilijuna dolara. Sa 20 milijuna bitcoina, svaki bi onda vrijedio oko 10 milijuna dolara."
Čak i da Bitcoin ne postane u cijelost globalan novac, nego da se samo natječe sa zlatom kao neovisno spremište vrijednosti, i dalje je masivno podcijenjen. Mapiranje tržišne kapitalizacije postojeće količine izrudarenog zlata (oko 8 trilijuna dolara) na maksimalnu dostupnost Bitcoina od 21 milijun, daje vrijednost od otprilike 380,000 dolara po bitcoinu. Kao što smo vidjeli u prethodnom tekstu, svojstva koja omogućavaju monetarnom dobru da bude prikladno spremište vrijednosti, čine Bitcoin superiornijim zlatu u svakom pogledu osim trajanja povijesti. No, kako vrijeme prolazi i Lindy efekt postane jači, dosadašnja povijest će prestati biti prednost zlata. Samim time, nije nerazumno očekivati da će Bitcoin narasti do, a možda i preko, ukupne cijene zlata na tržištvu do 2030. Opaska ovoj tezi je činjenica da veliki postotak vrijednosti zlata dolazi od toga što ga centralne banke čuvaju kao spremište vrijednosti. Da bi Bitcoin došao do te razine, određena količina suverenih država će trebati sudjelovati. Hoće li zapadnjačke demokracije sudjelovati u vlasništvu Bitcoina je nepoznato. Vjerojatnije je, nažalost, da će prve nacije u Bitcoin tržištu biti sitne diktature i kleptokracije.
Ako niti jedna država ne bude sudjelovala u Bitcoin tržištu, optimistična teza i dalje postoji. Kao nevisno spremište vrijednosti u rukama individualnih i institucionalnih ulagača, Bitcoin je i dalje vrlo rano u svojoj “krivulji prihvaćenosti” (adoption curve); tzv. “rana većina” ulaze na tržište sada, dok će ostali ući tek nekoliko godina kasnije. Sa širim sudjelovanjem individualnih i institucionalnih ulagača, cijena po bitcoinu između 100,000 i 200,000 dolara je sasvim moguća.
Posjedovanje bitcoina je jedna od malobrojnih asimetričnih novčanih strategija dostupnih svakome na svijetu. Poput “call” opcija, negativan rizik ulagača je ograničen na 1x, dok potencijalna dobit i dalje iznosi 100x ili više. Bitcoin je prvi istinski globalan balon čija je veličina ograničena samo potražnjom i željom građana svijeta da zaštite svoju ušteđevinu od raznovrsnih ekonomskih malverzacija vlade. Bitcoin je ustao kao feniks iz pepela globalne financijske krize 2008. godine - katastrofe kojoj su prethodile odluke centralnih banaka poput američke Federalne rezerve (Federal Reserve).
Onkraj samo financijske teze za Bitcoin, njegov rast i uspjeh kao neovisno spremište vrijednosti imat će duboke geopolitičke posljedice. Globalna, ne-inflacijska valuta će prisiliti suverene države da promjene svoje primarne mehanizme financiranja od inflacije u izravno oporezivanje; koje je daleko manje politički popularno. Države će se smanjivati proporcionalno političkoj boli koju im nanese oporezivanje kao jedini način financiranja. Nadalje, globalna trgovina vršiti će se na način koji zadovoljava aspiraciju Charlesa de Gaullea, da nijedna nacija ne bi smjela imati privilegiju nad ikojom drugom:
"Smatramo da je potrebno da se uspostavi međunarodna trgovina, kao što je bio slučaj prije velikih nesreća koje su zadesile svijet, na neosporivoj monetarnoj bazi, koja ne nosi na sebi oznaku ijedne države."
Za 50 godina, ta monetarna baza biti će Bitcoin.
-
 @ 554ab6fe:c6cbc27e
2025-01-22 17:57:30
@ 554ab6fe:c6cbc27e
2025-01-22 17:57:30In recent years, mindfulness meditation has been gaining traction as a form of therapy to address various health-related issues. In a previous blog post, I discussed how meditation is a promising technique to alleviate anxiety and depression. Previously, I examined the effects of mindfulness meditation through a psychological perspective. However, I find that the science of meditation is a hard sell for many people; people who come from a more scientific background often need to understand the underlying physiologic mechanisms of mindfulness meditation to be convinced of its efficacy. This is understandable -- I seek these kinds of answers as well. The science of meditation is still very new, and no one has a clear understanding of why it works. However, my research has led me to discover a few promising theories from a bottom-up point of view. How does the practice of meditation change the body, and do these changes then influence the state of the mind?
Meditation appears beneficial to the body, in part, because it increases parasympathetic nervous system (PNS) activity, and decreases sympathetic nervous system (SNS) activity. The SNS is activated during times of danger, and is often called the “fight or flight” response. This response is healthy in moments of danger but becomes detrimental when it is chronically activated. Modern life is full of stressors that keeps the SNS activated, and this chronic SNS activity is poor for our health. Meditation helps us decrease the activation though eliciting the ancillary PNS. But how? The two theories I will outline below all revolve around the effect slow breathing has on increasing parasympathetic activity through vagal tone. More specifically, these theories outline how breathing patterns affect the activation of baroreceptors within blood vessels, and mechanoreceptors within the lungs (Gerritsen & Band, 2018).
Baroreceptors are pressure sensors found within our body. These are important detectors within blood vessels that help relay sensory information to the brain for autonomic control, which helps maintain balance within the cardiovascular systems. For instance, inhalation causes an increase in heart rate, while exhalation causes the heart rate to slow. This is called respiratory sinus arrhythmia (RSA). The detection and signaling of this change, in part, is sensed by baroreceptors within the veins (Gary G. Berntson, John T. Cacioppo, 1993; Karemaker, 2009). The baroreceptors are activated when blood pressure increases in the aorta during exhalation due to increased intra-thoracic pressure. The activation signals a decrease in heart rate that causes a reduction in blood pressure, and vice versa (Gerritsen & Band, 2018; Lehrer & Gevirtz, 2014; Vaschillo et al., 2002). This is one example of the many methods in which balance is maintained within the cardiovascular system via the vagus nerve. Keep in mind that the sensitivity and responsiveness of these receptors can change, which thereby changes the frequency (or tone) of vagus nerve activation. It has been shown that decreasing one’s breath to 0.1 Hz (about 10 seconds per breath) increases the sensitivity of heart rate change given changes in blood pressure (Bernardi et al., 2001; Lehrer et al., 2003). This suggests that the baroreceptors become more sensitive during deep/slow breathing, and the vagus nerve is activated more often. Thus, breathing at this rate increases the sensitivity of these receptors, thereby increasing vagal tone.
Other research has also confirmed that slow breathing rates result in increased heart rate variability (HRV)(Song & Lehrer, 2003). As the name suggests, heart rate variability represents the variability of time intervals between consecutive heartbeats (Makivić et al., 2013). The heart changes speed given the demand of the body. This flexibility of the heart to change its speed quickly is known as heart rate variability. If the speed at which the heart beats changes is fast, the HRV is said to increase. This observation that slower breathing increases HRV makes sense because it is commonly used as an indicator of autonomic nervous system balance (Ernst, 2017) and is increased with increased vagal tone (Laborde et al., 2017). Consequently, because modern day stress causes us to go into “fight or flight” mode often, increasing SNS activity and decreasing PNS activity, decreased HRV can be used as an indicator of stress (Kim et al., 2018). This is important because this breathing frequency of 0.1Hz is the same breathing rate observed in novice Zen meditators (Cysarz & Büssing, 2005). Since meditation results in calmed breathing, it thereby increases vagal tone, and decreases the physiologic processes of stress.
In more simplistic terms, the pace of slowed and consistent breathing increases baroreceptor sensitivity which increases vagal tone because this nerve is what sends the signals of the receptors to the brain (Lehrer et al., 2003). Vagus nerve tone is a major driver of parasympathetic nervous system activity. Due to the vagus nerve innervating all major systems of the body, when activation is increased in one area, activation is increased in the rest. This counteracts the SNS activity caused by stress, which theoretically should balance the body and improve health.
The above theory describes how breathing patterns influence baroreceptors, which influence vagus nerve tone. Another theory argues that it is the receptors within the lungs that cause the physiologic changes(Noble & Hochman, 2019). Within the lungs, there are two pulmonary stretch receptors worth noting: rapidly-adapting receptors (RARs) and slowly-adapting receptors (SARs). RARs are typically activated throughout normal breathing(Noble & Hochman, 2019), while slower breathing additionally activates SARs(Jerath et al., 2006; Schelegle, 2003). SARs are important receptors as they are involved in the Hering-Breur Reflex(Schelegle, 2003), which is a reflex that induces immediate exhalation of the lungs after the detection of an excessively large inhale(Moore, 1927). This reflex likely exists to protect the lungs from overexpansion, but also highlights the importance of the role of these receptors in the nervous system’s control over the lungs.
SARs send signals to a region of the brain called the nuclear tractus solataris (NTS) via the vagus nerve(Schelegle, 2003). The NTS is a relay station for all vagal afferents(Noble & Hochman, 2019), and sends neuronal input to the hypothalamic paraventricular nucleus and the central nucleus of the amygdala(Petrov et al., 1993). The amygdala is highly involved in emotional regulation and processing(Desbordes et al., 2012). Increased amygdala activity is also associated with perceived stress(Taren et al., 2015). SARs activation either directly, or indirectly inhibits amygdala activation by means of the NTS(Noble & Hochman, 2019). This possibly explains how deep breathing can provide stress-reducing effects(Noble & Hochman, 2019).
These two ideas are not mutually exclusive theories. Both of the mechanisms may play a role in the benefits of mindfulness meditation and similar practices. At the same time, you may be noticing that there is a “chicken or egg” question here: are these changes happening because our mind decided to calm down first, or is the mind calming down because of the physical activity of mindfulness? This is surely a difficult question – however, perhaps it is frivolous. It is of my current opinion that both occur simultaneously. The mind and body are one. The practice of meditation induces both mental and physical changes, which in turn cause a positive feedback loop of relaxation. This parasympathetic activity has the potential to create resilience towards our modern, stressful environment. So, like the Yin Yang, these two ideas are not in opposition to each other, but rather represent a larger truth -- a truth that challenges us to become more considerate of our body, and work to bring it more calmness.
References
Bernardi, L., Gabutti, A., Porta, C., & Spicuzza, L. (2001). Slow breathing reduces chemoreflex response to hypoxia and hypercapnia, and increases baroreflex sensitivity. Journal of Hypertension, 19(12), 2221–2229. https://doi.org/10.1097/00004872-200112000-00016
Cysarz, D., & Büssing, A. (2005). Cardiorespiratory synchronization during Zen meditation. European Journal of Applied Physiology, 95(1), 88–95. https://doi.org/10.1007/s00421-005-1379-3
Desbordes, G., Negi, L. T., Pace, T. W. W., Alan Wallace, B., Raison, C. L., & Schwartz, E. L. (2012). Effects of mindful-attention and compassion meditation training on amygdala response to emotional stimuli in an ordinary, Nonmeditative State. Frontiers in Human Neuroscience, 6(OCTOBER 2012), 292. https://doi.org/10.3389/fnhum.2012.00292
Ernst, G. (2017). Heart-Rate Variability—More than Heart Beats? Frontiers in Public Health, 5, 1. https://doi.org/10.3389/fpubh.2017.00240
Gary G. Berntson, John T. Cacioppo, K. S. Q. (1993). Arritmia sinusal respiratória: argumentos autonômicos, mecanismos fisiológicos e implicações psicofisiológicas/Respiratory sinus arrhythmia: autonomic origins, physiological mechanisms and psychophysiological implications. In Psychophysiology (Vol. 30, pp. 183–196).
Gerritsen, R. J. S., & Band, G. P. H. (2018). Breath of Life: The Respiratory Vagal Stimulation Model of Contemplative Activity. Frontiers in Human Neuroscience, 12, 9. https://doi.org/10.3389/fnhum.2018.00397
Jerath, R., Edry, J. W., Barnes, V. A., & Jerath, V. (2006). Physiology of long pranayamic breathing: Neural respiratory elements may provide a mechanism that explains how slow deep breathing shifts the autonomic nervous system. Medical Hypotheses, 67(3), 566–571. https://doi.org/10.1016/j.mehy.2006.02.042
Karemaker, J. M. (2009). Counterpoint: Respiratory sinus arrhythmia is due to the baroreflex mechanism. Journal of Applied Physiology, 106(5), 1742–1743. https://doi.org/10.1152/japplphysiol.91107.2008a
Kim, H. G., Cheon, E. J., Bai, D. S., Lee, Y. H., & Koo, B. H. (2018). Stress and heart rate variability: A meta-analysis and review of the literature. In Psychiatry Investigation (Vol. 15, Issue 3, pp. 235–245). Korean Neuropsychiatric Association. https://doi.org/10.30773/pi.2017.08.17
Laborde, S., Mosley, E., & Thayer, J. F. (2017). Heart rate variability and cardiac vagal tone in psychophysiological research - Recommendations for experiment planning, data analysis, and data reporting. In Frontiers in Psychology (Vol. 8, Issue FEB, p. 213). Frontiers Research Foundation. https://doi.org/10.3389/fpsyg.2017.00213
Lehrer, P. M., & Gevirtz, R. (2014). Heart rate variability biofeedback: How and why does it work? Frontiers in Psychology, 5(JUL), 756. https://doi.org/10.3389/fpsyg.2014.00756
Lehrer, P. M., Vaschillo, E., Vaschillo, B., Lu, S.-E., Eckberg, D. L., Edelberg, R., Shih, W. J., Lin, Y., Kuusela, T. A., Tahvanainen, K. U. O., & Hamer, R. M. (2003). Heart Rate Variability Biofeedback Increases Baroreflex Gain and Peak Expiratory Flow. Psychosomatic Medicine, 65(5), 796–805. https://doi.org/10.1097/01.PSY.0000089200.81962.19
Makivić, B., Nikić, M. D., & Willis, M. S. (2013). Heart Rate Variability (HRV) as a Tool for Diagnostic and Monitoring Performance in Sport and Physical Activities. Journal of Exercise Physiology Online, 16(3), 103–131.
Moore, B. Y. R. L. (1927). A STUDY OF THE HERING-BREUER REFLEX . ( From the Hospital of The Rockefeller Institute for Medical Research .) The observation has been made by several investigators that a rapid respiratory rate depends on intact vagal conduction . In experiments on anes. 819–837.
Noble, D. J., & Hochman, S. (2019). Hypothesis: Pulmonary Afferent Activity Patterns During Slow, Deep Breathing Contribute to the Neural Induction of Physiological Relaxation. Frontiers in Physiology, 10, 1176. https://doi.org/10.3389/fphys.2019.01176
Petrov, T., Krukoff, T. L., & Jhamandas, J. H. (1993). Branching projections of catecholaminergic brainstem neurons to the paraventricular hypothalamic nucleus and the central nucleus of the amygdala in the rat. Brain Research, 609(1–2), 81–92. https://doi.org/10.1016/0006-8993(93)90858-K
Schelegle, E. S. (2003). Functional morphology and physiology of slowly adapting pulmonary stretch receptors. The Anatomical Record, 270A(1), 11–16. https://doi.org/10.1002/ar.a.10004
Song, H. S., & Lehrer, P. M. (2003). The effects of specific respiratory rates on heart rate and heart rate variability. Applied Psychophysiology Biofeedback, 28(1), 13–23. https://doi.org/10.1023/A:1022312815649
Taren, A. A., Gianaros, P. J., Greco, C. M., Lindsay, E. K., Fairgrieve, A., Brown, K. W., Rosen, R. K., Ferris, J. L., Julson, E., Marsland, A. L., Bursley, J. K., Ramsburg, J., & Creswell, J. D. (2015). Mindfulness meditation training alters stress-related amygdala resting state functional connectivity: a randomized controlled trial. Social Cognitive and Affective Neuroscience, 10(12), 1758–1768. https://doi.org/10.1093/scan/nsv066
Vaschillo, E., Lehrer, P., Rishe, N., & Konstantinov, M. (2002). Heart rate variability biofeedback as a method for assessing baroreflex function: A preliminary study of resonance in the cardiovascular system. Applied Psychophysiology Biofeedback, 27(1), 1–27. https://doi.org/10.1023/A:1014587304314
-
 @ 93eeb56c:9469e39a
2025-01-22 17:08:44
@ 93eeb56c:9469e39a
2025-01-22 17:08:44💀 Introducing No Good Kid
After 15 years of working as a graphic designer, marketer, and brand therapist, I recently started to feel the urgency to start a project of my own.
I feel out of tune with the state of mainstream marketing today—sterile aesthetics, overstated presentations, and endless battle for attention on centralized social media.
So, I’m introducing No Good Kid. And as you can guess from the title, No Good Kid targets both creators and audiences who don’t exactly fit the status quo.
No Good Kid is the creative’s alter ego. It’s an identity that can be shared and serves as a label under which we can collaborate to create cool projects.
🪩 What is it?
I think of it as an identity—the creative’s alter ego, if you will—that can be shared among creators and serve as a label under which we can collaborate and create.
And the result can be anything, from a marketing campaign to original music production. There are no borders. If the party is right, anything can happen.
In the spirit of gamma personalities, there will be no agency, leader, or hierarchy.
My hope is that the projects will reflect values such as freedom and solidarity. But it’s entirely up to the creators.
Feel free to use the No Good Kid identity, share your project, or reach out if I can help.
🔥 Projects released so far

whistleblower10
In 2024, I crafted a campaign for Amnesty International CZ which led to Amnesty accepting Bitcoin donations for a limited time.
whistleblower10 website→\ project design→

The Nocoiner Syndrome
By the end of last year, The Nocoiner Syndrome was published by Institute of Cryptoanarchy—a research paper written by Peter Horváth that rebutted the ECB’s statement about Bitcoin being on “the road to irrelevance.”
Institute of Cryptoanarchy website→\ project design→
☮️ Vision
There is no need to place a label on this project. I want No Good Kid to be a tool to connect beliefs and hopes with skills in the name of freedom.
Let me know what you think of the idea, or if you have a project in mind.
Be well, and stay no good.
dworis 💀
🥁 Follow No Good Kid:
https://nogoodkid.com/ npub1j0ht2m9jgs6mccyvkffd2dlnfusmqfx9mjlwg6fsmfwxm9rfuwdq40w6rf npub1uwglfjet0m2regqhmgeygc2tc75ngezl8fhftgzhaqas9rjeny8sdztml4
---
🔥 Thanks for reading
Enjoyed this article?
⚡️ Zap some sats
literalpersian75(at)walletofsatoshi.com💀 No Good Kid projects & portfolio
https://nogoodkid.com/👥 Let’s connect on Nostr
npub1j0ht2m9jgs6mccyvkffd2dlnfusmqfx9mjlwg6fsmfwxm9rfuwdq40w6rf -
 @ eee391ee:8d0b97c2
2025-01-22 16:42:17
@ eee391ee:8d0b97c2
2025-01-22 16:42:17Amber 3.1.9
- Add missing logs for relay errors
- Change listen for new connections button text and icons
Download it with zap.store, Obtainium, f-droid or download it directly in the releases page
If you like my work consider making a donation
Verifying the release
In order to verify the release, you'll need to have
gpgorgpg2installed on your system. Once you've obtained a copy (and hopefully verified that as well), you'll first need to import the keys that have signed this release if you haven't done so already:bash gpg --keyserver hkps://keys.openpgp.org --recv-keys 44F0AAEB77F373747E3D5444885822EED3A26A6DOnce you have his PGP key you can verify the release (assuming
manifest-v3.1.9.txtandmanifest-v3.1.9.txt.sigare in the current directory) with:bash gpg --verify manifest-v3.1.9.txt.sig manifest-v3.1.9.txtYou should see the following if the verification was successful:
bash gpg: Signature made Fri 13 Sep 2024 08:06:52 AM -03 gpg: using RSA key 44F0AAEB77F373747E3D5444885822EED3A26A6D gpg: Good signature from "greenart7c3 <greenart7c3@proton.me>"That will verify the signature on the main manifest page which ensures integrity and authenticity of the binaries you've downloaded locally. Next, depending on your operating system you should then re-calculate the sha256 sum of the binary, and compare that with the following hashes:
bash cat manifest-v3.1.9.txtOne can use the
shasum -a 256 <file name here>tool in order to re-compute thesha256hash of the target binary for your operating system. The produced hash should be compared with the hashes listed above and they should match exactly. -
 @ 4506e04e:8c16ba04
2025-01-22 16:37:08
@ 4506e04e:8c16ba04
2025-01-22 16:37:08If you are a researcher in the field of medicine, you are most likely very familiar with PubMed – where you get citations for the articles and studies that drive your work forward. PubMed Central (PMC), the full-text repository of life sciences journal literature managed by the National Library of Medicine (NLM), was established in 2000. Its creation marked a significant milestone in providing open access to biomedical research. Since 2005, PMC has served as the designated repository for papers submitted under the NIH Public Access Policy, reflecting the growing emphasis on transparency and accessibility in scientific research. Over the years, PMC has expanded its scope, becoming a repository for papers aligned with public and open access policies from various research funding organizations, both within and beyond biomedical sciences.
Funding and Partnerships
NLM’s operations, including PubMed and PMC, are supported by a combination of government funding and contributions from influential entities such as The Bill & Melinda Gates Foundation.
The Bill and Melinda Gates Foundation receives significant donations from pharmaceutical companies, as well as other organizations and individuals. The exact amount of money donated by each company can vary from year to year, but here are some examples of the amounts donated by the pharmaceutical companies:
GSK (GlaxoSmithKline):
- In 2020, GSK donated $100 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, GSK donated $50 million to the Gates Foundation to support the development of a new malaria vaccine.
Pfizer:
- In 2020, Pfizer donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, Pfizer donated $25 million to the Gates Foundation to support the development of a new malaria vaccine.
Merck & Co.:
- In 2020, Merck donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, Merck donated $25 million to the Gates Foundation to support the development of a new malaria vaccine.
Novartis: - In 2020, Novartis donated $20 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis. - In 2019, Novartis donated $10 million to the Gates Foundation to support the development of a new malaria vaccine.
Johnson & Johnson:
- In 2020, Johnson & Johnson donated $50 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria, tuberculosis, and HIV/AIDS.
- In 2019, Johnson & Johnson donated $25 million to the Gates Foundation to support the development of a new malaria vaccine.
Sanofi:
- In 2020, Sanofi donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis.
- In 2019, Sanofi donated $10 million to the Gates Foundation to support the development of a new malaria vaccine.
AstraZeneca:
- In 2020, AstraZeneca donated $20 million to the Gates Foundation to support the development of new vaccines and treatments for diseases such as malaria and tuberculosis.
- In 2019, AstraZeneca donated $10 million to the Gates Foundation to support the development of a new malaria vaccine.
Eli Lilly and Company:
- In 2020, Eli Lilly donated $10 million to the Gates Foundation to support the development of new treatments for diseases such as malaria and tuberculosis.
- In 2019, Eli Lilly donated $5 million to the Gates Foundation to support the development of a new malaria vaccine.
Additionally, NLM website [https://cdn.ncbi.nlm.nih.gov/pmc/cms/files/PMCFunderDepositList.xlsx] (list over 200)(!) organisations that are founding it. What could go wrong one might ask?!
The Centralization Challenge
While PubMed and PMC have played a pivotal role in democratizing access to scientific literature, their centralized nature presents vulnerabilities. Over the past century healthcare has grown to become one of the most profitable industries and to believe that the healthcare system we have today is the best we can do is far from understatement.
PubMed's reliance on centralized funding and decision-making processes makes it susceptible to external influences, including lobbying by powerful entities. Moreover, the centralized infrastructure allows for content to be published and removed with relative ease, often without leaving a trace. This raises concerns about the integrity and permanence of the scientific record, particularly in contentious or politically sensitive areas of research.
The ability to alter or erase information from PubMed undermines trust in the system’s objectivity and neutrality. Researchers and the public alike depend on these repositories for reliable and impartial access to scientific knowledge. Any perceived or actual manipulation of content can erode confidence in the platform and compromise its foundational mission.
The Case for Decentralization
To address these challenges, a decentralized alternative built on emerging technologies, such as the Nostr protocol, could offer significant advantages. A decentralized platform would:
-
Enhance Resilience: By distributing data across a network of relays, a decentralized system would eliminate single points of failure, ensuring the scientific record remains intact and always accessible even in the face of technical or political disruptions.
-
Increase Transparency: Decentralized systems inherently log changes, making it nearly impossible to alter or remove content without leaving an auditable trail. This transparency would bolster trust in the integrity of the research.
-
Reduce Susceptibility to Lobbying: Without centralized control, the influence of external entities on the platform’s content would be significantly diminished, preserving the objectivity of the scientific record.
-
Foster Open Collaboration: A decentralized approach aligns with the principles of open science, encouraging global collaboration without the constraints of centralized oversight or bias introduced by big pharma lobby.
Conclusion
While PubMed and PMC have been instrumental in advancing access to scientific literature, their centralized nature leaves them vulnerable to manipulation and external pressures. A shift toward a decentralized, censorship-resistant platform would address these vulnerabilities and provide a more robust and trustless repository for scientific knowledge. Groundbreaking research that dares to challenge the pharmaceutical industry's status quo could be published anonymously, following in the footsteps of the Bitcoin whitepaper's pseudonymous author, Satoshi Nakamoto. Leveraging technologies like the Nostr protocol, the research community can build a system that ensures the permanence, integrity, and impartiality of the scientific record for generations to come.
-
 @ 000002de:c05780a7
2025-01-22 16:33:59
@ 000002de:c05780a7
2025-01-22 16:33:59Anyone else noticing their LN address not working with Minibits?
originally posted at https://stacker.news/items/860143
-
 @ b83e6f82:73c27758
2025-01-22 16:29:15
@ b83e6f82:73c27758
2025-01-22 16:29:15Citrine 0.7.1
- Add the restore follows button back
- Show notification when backing up database
- Listen for pokey broadcasts
Download it with zap.store, Obtainium, f-droid or download it directly in the releases page
If you like my work consider making a donation
Verifying the release
In order to verify the release, you'll need to have
gpgorgpg2installed on your system. Once you've obtained a copy (and hopefully verified that as well), you'll first need to import the keys that have signed this release if you haven't done so already:bash gpg --keyserver hkps://keys.openpgp.org --recv-keys 44F0AAEB77F373747E3D5444885822EED3A26A6DOnce you have his PGP key you can verify the release (assuming
manifest-v0.7.1.txtandmanifest-v0.7.1.txt.sigare in the current directory) with:bash gpg --verify manifest-v0.7.1.txt.sig manifest-v0.7.1.txtYou should see the following if the verification was successful:
bash gpg: Signature made Fri 13 Sep 2024 08:06:52 AM -03 gpg: using RSA key 44F0AAEB77F373747E3D5444885822EED3A26A6D gpg: Good signature from "greenart7c3 <greenart7c3@proton.me>"That will verify the signature on the main manifest page which ensures integrity and authenticity of the binaries you've downloaded locally. Next, depending on your operating system you should then re-calculate the sha256 sum of the binary, and compare that with the following hashes:
bash cat manifest-v0.7.1.txtOne can use the
shasum -a 256 <file name here>tool in order to re-compute thesha256hash of the target binary for your operating system. The produced hash should be compared with the hashes listed above and they should match exactly. -
 @ 8d34bd24:414be32b
2025-01-22 15:27:34
@ 8d34bd24:414be32b
2025-01-22 15:27:34When I read this verse, I saw something I had never seen before.
A servant who acts wisely will rule over a son who acts shamefully,\ And will share in the inheritance among brothers. (Proverbs 17:2)
I had taken this by its plain meaning about a servant and a son and how they will be treated based on their actions, but I think there is more to this. In the Old Testament, the Bible hints at God’s plan for mankind which would include more than just God’s chosen people, Israel.
since Abraham will surely become a great and mighty nation, and in him all the nations of the earth will be blessed? (Genesis 18:18)
In the New Testament, this prediction is expanded upon:
The Scripture, foreseeing that God would justify the Gentiles by faith, preached the gospel beforehand to Abraham, saying, “All the nations will be blessed in you .” (Galatians 3:8)
All nations will be blessed through Abraham and Jacob, especially through Israel.
What does the Bible say about the relationship between Jews, gentiles, and salvation?
I say then, they [Jews/Israel] did not stumble so as to fall, did they? May it never be! But by their transgression salvation has come to the Gentiles, to make them jealous. Now if their transgression is riches for the world and their failure is riches for the Gentiles, how much more will their fulfillment be! But I am speaking to you who are Gentiles. Inasmuch then as I am an apostle of Gentiles, I magnify my ministry, if somehow I might move to jealousy my fellow countrymen and save some of them. For if their rejection is the reconciliation of the world, what will their acceptance be but life from the dead? If the first piece of dough is holy, the lump is also; and if the root is holy, the branches are too.
But if some of the branches were broken off, and you, being a wild olive, were grafted in among them and became partaker with them of the rich root of the olive tree, do not be arrogant toward the branches; but if you are arrogant, remember that it is not you who supports the root, but the root supports you. You will say then, “Branches were broken off so that I might be grafted in.” Quite right, they were broken off for their unbelief, but you stand by your faith. Do not be conceited, but fear; for if God did not spare the natural branches, He will not spare you, either. Behold then the kindness and severity of God; to those who fell, severity, but to you, God’s kindness, if you continue in His kindness; otherwise you also will be cut off. And they also, if they do not continue in their unbelief, will be grafted in, for God is able to graft them in again. For if you were cut off from what is by nature a wild olive tree, and were grafted contrary to nature into a cultivated olive tree, how much more will these who are the natural branches be grafted into their own olive tree? (Romans 11:11-24)
The Jews are God’s chosen people, but many have rejected their God and Savior. Because of this, God cut off their branch from the root and grafted in chosen gentiles. The new vine is made up of both Jew and gentile.
Now let’s look back at the verse I started with:
A servant who acts wisely will rule over a son who acts shamefully,\ And will share in the inheritance among brothers. (Proverbs 17:2)
Could God be warning the Israelites, that if they act shamefully, they will have to share their inheritance with the gentiles who will partake of the blessings of God towards His chosen people?
Obviously God had a plan. He knew every choice every person would make and is able to control any decision He wishes. Still, I think this was a warning to Israel. Just as I never saw it when reading this verse many times, the Jews didn’t see the warning because they thought their position was secure despite their actions. Those who are truly chosen and are truly children of God, will choose to serve and obey God. They will not reject Him. They may make mistakes, but they will always turn back to Him and seek to serve and please Him.
I pray that you will be or are grafted into the true vine, Jesus Christ our Savior.
Trust Jesus.
-
 @ 21ac2956:09d1e2df
2025-01-22 15:27:00
@ 21ac2956:09d1e2df
2025-01-22 15:27:00kakoi の仕様についてのメモ
キーボード操作
- 左手での操作に最適化
| キー | 動作 | |:-|:-| | ESC | 設定画面 | | F1 / F12 | ポストバーの表示と非表示 | | F2 | 時間の表示と非表示 | | F3 | ユーザーアイコンの表示と非表示 | | F4 | 名前の表示と非表示 | | F5 | Geminiによるタイムラインまとめ画面を表示 | | F9 / Z | コンテンツの折り返し表示の切り替え (余白ダブルクリックでも動作) | | F10 | ユーザーリストとキーワード通知の設定画面 (余白右クリックでも動作) | | F11 | メイン画面の表示と非表示 (ポストバー表示) | | Shift + W | イベント最上行へ移動 | | W / ↑| イベント選択上移動 | | S / ↓ | イベント選択下移動 | | Shift + S | イベント最下行へ移動 | | A / ← | Webビューを開く (イベントを右クリックでも動作) | | F / → | リアクションを送信 (イベントをダブルクリックでも動作) | | 1 ~ 0 | リアクションを選択 | | R | 返信 | | B | リポスト | | Q | 引用 | | C | Webビューを閉じる | | Ctrl + Shift + A | メイン画面をアクティブにする |
タイムライン
- kind:1, 6, 7, 16を取得して表示する
- フォロイーの名前の前には * が付く
フォローリスト(kind:3)
-
参照のみで更新はしない
-
F10 で開くユーザーリストでユーザーを選択し petname セルをクリックすることで未フォローユーザーにもペットネームを設定可能(ローカル保存)
プロフィール(kind:0)
- F10 で開くユーザーリストでユーザーを選択し picture セルをクリックすることでユーザーのアイコン表示を変更可能(ローカル保存)
返信(NIP-10 kind:1)
- kakoi のタイムラインに流れるすべてのイベント種に返信可能とする
- スレッドを考慮せず、単一イベントへの単発返信とする
- e タグは marker と返信先 pubkey は設定していない。 relay-url には空文字を設定
json ["e", "返信先 event-id", ""]- p タグは 返信先 pubkey ひとつだけを指定
リポスト(NIP-18 kind:6 , 16)
- kakoi のタイムラインに流れるすべてのイベント種をリポスト可能
- kind:1はkind:6。その他はkind:16でリポストする
- e タグは relay-url に空文字を設定
json ["e", "リポスト元 event-id", ""]引用(NIP-18 kind:1)
- q タグは relay-url に空文字を設定
json ["q", "引用元 event-id", ""] -
 @ 6b57533f:eaa341f5
2025-01-22 13:53:03
@ 6b57533f:eaa341f5
2025-01-22 13:53:03Erik Prince · 30 April 2024
How the MIC and the Neocons Keep America Losing
It is painfully apparent to anyone of sound mind and judgment that there’s something gravely wrong with America’s current military capacity and our ability to project power in the world. The WWII-era fighting force composed of fourteen million GIs with a muscular industrial base backing them up is almost unimaginable today. In the last three years, five different US embassies have been hastily evacuated: Sudan, Afghanistan, Belarus, Ukraine, and Niger. Americans are held hostage in Gaza; commercial shipping traffic is blockaded and our ground and naval forces are shot at daily with impunity. How did America go from winning the Cold War and becoming the sole global superpower in the 90s to the state of disarray that we find ourselves in now?
One reason is financial. All warfare has an underlying economic basis and a nation’s military power reflects its economic structure. Today in America the “exorbitant privilege” of the US dollar and the unlimited printing press of fiat currency it enables means current US defense spending is essentially covered by debt: indeed at least 30% of the current national debt consists of military overspend from the so-called Global War on Terror. This reality has created an absence of strategic discipline, and a military policy that prioritizes a tiny guild of contractors feeding an obese top-heavy structure rather than winning wars.
The roots of the current situation reach back to the election of Reagan in 1980. Reagan started a pivot from 35 years of containment to a more aggressive approach, covered by deficits. Channeled economically, politically, culturally, socially, and through covert action these measures helped to bring an end to the Soviet Union, but at a critical strategic cost. Partly as a consequence of the central economic role that the USSR had come to play for the US defense industry, the opportunity to positively engage with Russia after 1991 was rejected by the dominant neoconservative faction and their military-industrial complex allies in Washington. Originally Trotskyites, the Neocons had taken root in the corporatist wing of the Republican Party and gradually increased in influence, to eventually become dominant in the Washington Beltway foreign policy and emblematic of its mentality of continuous warfare funded by an unlimited fiat printing press.
The so-called “Peace Dividend” that followed the end of the Cold War was redirected into expanding NATO instead of ending it. The goal was to enrich the military-industrial complex by creating more clients to buy US weapons, at the expense of the opportunity to partner with Russia. Promises of not expanding NATO eastward into former Warsaw Pact countries were broken and NATO troops were deployed on Russia’s border.
The priorities of Neocon Washington were also projected into US policy in Africa. After Liberian warlord Charles Taylor sponsored the Revolutionary United Front (RUF) in Sierra Leone in the late ’90s, the RUF quickly captured most of the country, particularly the diamond-rich areas of the north. In the process they committed atrocious acts of savagery against Sierra Leone’s civilian population. Into this maelstrom entered Executive Outcomes (EO), a South African PMC. EO initially deployed 60 ex-South African Special Forces personnel fresh from ending a civil war that had raged for years in Angola, and eventually expanded to around 200 well-trained personnel. Using mostly equipment abandoned by Sierra Leone’s disintegrated army, within 6 months they’d retaken the country and restored peace and order to the extent that free and fair elections could be held 3 months later.
Executive Outcomes was sponsored by an association of diamond miners who wanted their mines back. This group was willing to sponsor an ongoing 30-man EO presence to retrain a new Sierra Leone armed forces while providing a backstop in case the rebels returned. Susan Rice, then Bill Clinton’s Assistant Secretary of State for Africa, vetoed this proposal: “We don’t want any white mercenaries in Africa,” she declared. The result? Within months the RUF and a new group called the West Side Boys had returned, killing, looting, and pillaging the country. 11,000 UN Peacekeepers at a cost of $1B+ per year in 1990s US dollars were now deployed. But they didn’t solve the problem, and not until the British SAS killed hundreds of rebels during a large hostage rescue mission of Irish Peacekeepers did the country start to stabilize.
This debacle in West Africa occurred on the heels of an even greater catastrophe further East. In the spring of 1994, after decades of simmering ethnic hatred in Rwanda, the Hutus launched a program of manual genocide. Over a four-month period they killed almost 1,000,000 of their Tutsi neighbors, a murder rate exceeding 8,000 per day, mainly using machetes and farm tools. Here as well EO made a formal proposal to the UN and the US government to intervene and prevent further slaughter. The proposal was also rejected by Rice in Washington. EO stayed out and the carnage continued unabated until Paul Kagame’s exiled Rwandan Patriotic Front invaded from Uganda and retook the country.
By the late 90s, with Washington engaged in combat in the former Yugoslavia, a new kind of enemy was emerging: jihadist Islam. In 1993 a poorly conceived and badly executed nation-building exercise in Somalia had already supplied a foretaste when the Battle of Mogadishu resulted in the death of 18 US Special Operations personnel and 73 wounded after repeated requests for air support were rejected by an indecisive Clinton administration. By 1999, unanswered attacks in Nairobi, Dar As Salaam, Saudi Arabia, Yemen and New York had claimed hundreds of lives and mauled a US Destroyer, USS Cole. Finally, on Sept 11th, 2001, this series of body blows reached its spectacular culmination.
In the aftermath of 9/11, President Bush met with his War Cabinet to plan a response to the costliest attack on American soil since Pearl Harbor. As the Pentagon smoldered, the Department of Defense recommended a bombing campaign and a Ranger raid against an Al Qaeda-linked farm, but wanted to wait at least six months before beginning combat operations in order to avoid the Afghan winter. The CIA, for their part, recommended an Unconventional Warfare campaign. They wanted to supercharge the Northern Alliance, who’d been fighting the Taliban for a decade, with US airpower directed by SOF advisors. The CIA plan was adopted. The Taliban and their guests Al-Qaeda were routed in weeks by a highly aggressive SOF targeting cycle which gave them no quarter.
The US response to 9/11 should have resembled a Scipio Africanus-style Roman punitive raid, killing all Taliban and Al-Qaeda remnants within reach, including those sheltering in the tribal areas of Pakistan, and then withdrawing. Instead, the Neocons saw a lucrative opportunity to ‘nation build’. Because the Pentagon runs on the bureaucratic principle of budget cycles and the internal war for promotion rather than the principle of victory, a vastly inflated occupational army ultimately comprising 120,000 soldiers was deployed to the country. This force represented a repetition of the failed Soviet plan of the 80s, to the extent of occupying the same bases.
Ignoring every historical lesson of successful counter-insurgencies, experienced soldiers were rotated on 6-12 month intervals with fresh units, losing all continuity and local intelligence. The top commander spot rotated 18 times in 20 years. Concerned as per usual with marketing for their defense contractor clients, the Neocons dragged dozens of largely unwilling NATO members to Afghanistan, producing a dysfunctional chaos of individual national mandates. Many nations wouldn’t patrol at night or engage in offensive combat missions. When the German army arrived in Kabul in the spring of 2002, among their concerns was finding appropriate housing for all the gay couples deployed in the Bundeswehr.
The Neocon plan for Afghanistan, or at least the story, was to impose a centralized Jeffersonian democracy on a largely illiterate, semi-feudal tribal nation by throwing infinite money at a paper-thin civil society. The result, unsurprisingly, was corruption, not infrastructure. Meanwhile, the military operation remained chaos incarnate. Not only was there never a truly empowered supreme commander, but authorities were split between the US Ambassador, CIA Station chief, the current 4-star US General, the CENTCOM Commander and their staff residing in Qatar or Tampa, and various representatives from NATO. This committee from Hell produced predictable results.
In the 1980s the US provided lethal aid to the Mujahedeen fighting the Soviets running to $1B a year including state-of-the-art Stinger missiles, which knocked down an average of one Soviet aircraft per day. Nobody provided this kind of aid to the Taliban: not one NATO/Coalition aircraft was lost to a guided missile. But air supremacy wasn’t enough. The Taliban were a self-funded insurgency composed of mostly illiterate fighters using weapons designed more than 70 years earlier. Although they lacked the techno-wizardry of the Pentagon forces, their budget grew to approximately $600mm per year from tolling narcotics and the import of fuel used to feed a thirsty Pentagon presence. Fuel logistics alone cost the Pentagon tens of billions per year, despite the fact that a vast reserve of crude – Amu-Darya Field in Balkh Province Afghanistan – had been drilled, proven and properly cemented by Soviet forces before they left in 1989. But what could have supplied the entire Afghanistan operation with low-cost, reliable hydrocarbon energy was ignored in favor of paying, by the time the fuel reached the vehicles, an operational cost of $250 per gallon. President Reagan and Mikhail Gorbachev sign the Intermediate Range Nuclear Forces Treaty (1987) / President George H.W. Bush talks to reporters about US military operations in Iraq, flanked by Defense Secretary Dick Cheney and Chair of the Joint Chiefs Colin Powell (1991) / George Bush with Dick Cheney and senior staff in the President’s Emergency Operations Center in Washington in the hours following the 9/11 attacks (2001) It’s fair to compare the longevity of the Soviet-built Afghan forces, holding on for years after the Soviets left, versus the Pentagon-built Afghan forces collapsing only weeks after the American withdrawal. Today of course the Taliban rule Afghanistan with an iron sandal. The trillions of dollars and thousands of lives expended by America’s youth were completely wasted – and nobody has ever been held to account. The Taliban have not become more moderate – they are exactly the same group as before and hosting more terror groups than ever. Al Qaeda is resident once again in Kabul, and now known to be gathering means to enrich uranium in Afghanistan.
Afghanistan wasn’t even the worst US military failure over the last twenty years. Almost exactly the same Neocon fever dream also played out in Iraq. Here again the fantasy of deposing a dictator in the name of installing democracy in a country with a culture with no history of representative democracy followed its inevitable course. After an initial phase of 24/7 war porn of the US invasion, broadcast by the network media through “embedded journalists,” the Pentagon was quickly dragged into an urban counter-insurgency quagmire involving a Sunni faction rebranded as Al Qaeda in Iraq, Saddam regime holdovers, and Shia insurgents, armed, trained and sometimes led by the Iranian Revolutionary Guard Corps.
This development was not inevitable. I still recall a sliding door moment early in the conflict when the Director of the Iraqi National Intelligence Service came to see me with his CIA liaison officer in early 2004. He described the scale of the efforts by the IRGC Quds Forces to infiltrate Iraqi society and establish a proxy capability similar to Hezbollah in Lebanon and requested that we develop a joint program to locate and eradicate the Iranian presence. Unfortunately, the program was blocked by then-National Security Advisor Condoleezza Rice, on the grounds that Iran was not our enemy and that the US must support the political process in Iraq. In the event, this political process spun into a vicious civil war, killing hundreds of thousands of civilians. Meanwhile, our ‘non-enemy’ Iran flooded the country with thousands of lethal EFP roadside bombs, to shred armored vehicles with American soldiers inside.
Today Iraq is subjugated by Iran with Tehran making key decisions and approving all key ministry appointments, including who becomes Prime Minister. Their power is backed by the Popular Mobilization Units (PMU) or Hashd al Shabi – an Iranian-controlled proxy mirroring Hezbollah in Lebanon. The PMUs are paid for by the Iraqi Government, armed in most cases with American weapons, and led either by Iranian-appointed commanders or by serving IRGC officers directly.
Source: The Stockholm International Peace Research Institute, 2021 America continues to wage futile forever wars of convenience because Washington believes we are immune to reality and evolved beyond history. The grand strategy of the so-called Global War on Terror was conceived on a false premise promoted by Neocon think tanks and the Military-Industrial Complex that American drone technology could revolutionize counter-insurgency warfare through surgical strikes targeting only the leadership of terror organizations. This delusion produced sclerosis in the military by stripping authority away from field commanders concerning when to shoot and when to hold fire. A fixation on large orbiting cameras likewise devolved into high-tech voyeurism with lawyers, not commanders making battlefield decisions even when friendly troops were in peril and requiring urgent air support.
Ultimately, the paradigm flies in the face of the realities of war. Leaders are replaceable. There’s always another ambitious jihadi looking to wear the crown of command. What actually ends wars is destroying enemy manpower, finance, logistics, and ability to resupply. Every relevant historical example tells the same story, from the wars of ancient Greece to continental European and Napoleonic wars to the American Civil War and the world wars of the 20th Century. In the course of losing WWII Germany lost 5.3 of 17.7 million men aged 15-44 years old, or 30% of their male population. This brutality is the reality of winning wars – as the recent US track record of failure shows. The “measured and proportional response” crowd wants a war without war. It’s a fantasy that only seems plausible to people who have never experienced war and are insulated from its consequences; their first-born children should be drafted into frontline combat units to relieve them of this problem.
After the Roman Empire lost a crushing defeat at the Battle of Cannae, the Roman Senate immediately became 40% undermanned, because the Roman leaders actually served in the defense of their Republic and risked their lives in battle for it. Today, America’s elites instead spend their time on Wall Street or in think tanks gathering degrees and attending conferences. The old concept of noblesse oblige has gone missing from our national culture and so has the concept of accountability.
Despite the failures of Iraq and Afghanistan, there have been zero lessons learned or course corrections made. Consequently, the failures keep coming. When Hamas unleashed thousands of rockets, missiles, paragliders, and ground assaults across 30 breach points into Israel on October 7 of last year, they showed how dangerous complacency can be. Clearly Hamas had plotted their operation for years. Their network of 300 miles of tunnels spanning all of Gaza was built with one goal in mind: to suck the IDF into an urban quagmire in order to maximize carnage and casualties, of both Palestinian civilian and Israeli soldiers. But why not flood the tunnels with seawater using Texas precision drilling technology? The tactic would have obviated the need to bomb urban areas containing civilians and the terrible suffering that this tactic entails. Flooding the tunnels would have destroyed all underground weapons storage, prevented maneuver, and would have forced Hamas to move or lose their hostage human shields.
In fact, an entire package of drilling/pumping and technical support for precisely this tactic was offered by donors to the IDF. Yet the IDF – under pressure from the Pentagon diktats – instead chose bombing. The result has seen a wave of global sympathy generated for the Palestinian cause and left Hamas in charge of uncleared southern Gaza: a double nightmare scenario far from being resolved.
Source: The Stockholm International Peace Research Institute, 2021
In 2011, Hillary Clinton, chief Neocon of the Obama Administration, proudly declared of Libya’s US-sponsored revolution: “We came. We saw. He died.” Colonel Qaddafi may not have been perfect but Libya under him was politically stable. Now? For 13 years the country has been wracked by civil war and chaos. Rife with Russian and Turkish PMCs fighting for regional hegemony, the country is now a major exporter of weapons and one of the biggest channels to Europe for drugs and human trafficking.
Further east, Iran, with Hamas, Hezbollah, Hashd al shaabi (Iraq), and the Houthis in Yemen, have built a powerful network of regional proxy forces, now extending even into South America through the Lebanese diaspora in the narcotics and weapons trade. In Yemen, the Houthis have developed into effective pirates, shutting off Red Sea shipping traffic with long-range anti-ship weapons hidden in Yemen’s rugged terrain. As a result, an already economically struggling Egypt – a key American ally – has suffered a 40% blow to their GDP from lost Suez transit fees of $800mm/month and everyone else has seen punishing supply chains inflation from dislocated transit routes and runaway insurance premiums.
Why are Iranian surrogates in Iraq and Yemen being permitted to fire hundreds of precision drones, cruise and ballistic missiles at US forces on land and sea, largely without meaningful response from Washington? What response there has been has mainly consisted of announcing a coalition named ‘Prosperity Guardian’ to protect shipping which collapsed almost immediately after multiple vessels were struck and destroyed. Why are US policymakers and the Pentagon unable to innovate effective military solutions?
It doesn’t have to be this way. In the 1960s, Egypt, then a Soviet client, seized half of Yemen and deposed the Yemeni monarch. In response, Britain and Saudi Arabia hired SAS founder David Stirling’s PMC Watchguard International. Within months they had sufficiently amplified the Yemeni Tribesman fighting capabilities to force Egypt to withdraw. Stirling actually received a medal from the IDF for engaging so many Egyptian troops that it assisted the IDF victory in the 1967 Six-Day War. Fast forward to 2017, Saudi Arabia and the UAE were trying to battle Iranian surrogate Houthis who seized control over half of Yemen. They request PMC support to replicate the successful Stirling model from the 1960s, and once again they are blocked, this time by Neocon Secretary of Defense Matthis serving under President Trump. The Houthis remained unchecked and ascendant, and eventually strong enough to shut off one of the world’s major trade routes.
Meanwhile this same approach is still failing in Africa. There have been a staggering nine coup d’etats across Africa in the last 4 years, mainly in ex-colonial French regions, where decades-long insurgencies have exploded following the destruction of Libya. The looting of massive Libyan state arsenals following the overthrow of Qaddafi flooded the region with weapons. Long insufficient COIN operations by France and their USG partners reached the end of the road; local militaries ousted their Paris-sponsored leadership. The current US humiliation in Niger and Chad where US forces are being forced to vacate new multi-billion dollar facilities built to support drone operations across Africa is the result.
Compare this to Russia. Having embraced PMC capabilities, Russia is currently running a successful playbook in Africa against ineffective Western-friendly governments by showing a firmer hand against jihadists. This cycle will continue unabated so long as the State Department and the CIA restrict their thinking to coming up with PR strategies while America’s rivals implement military solutions.
The Central African Republic, rich in buried mineral wealth, suffered a descent into civil war in 2014 and the empowerment of criminal gangs; the Seleca and Anti Balaka. In 2017, the CAR government requested Western PMC assistance to build a robust mining police force in order to choke out the gangs. Contracts were even signed and funding-ready. But once again this solution was blocked by the NeoCons at the State Dept and their pet, the UN, refusing to waive their sanctions against CAR for the purchasing of small arms to equip police. But Russia had no such issues and sent 400 Wagner personnel immediately. Now multiple Wagner units run mines that net the Russian PMC billions of dollars per year, funding many of their other operations across Africa.
Somalia has been a geopolitical problem since the early 90s, sucking up tens of billions in ineffective foreign aid, killing hundreds of thousands, exporting terrorism, sheltering pirates, and flooding America with hundreds of thousands of migrants. In the spring of 2020, Kenyan President Jomo Kenyatta reached out for private sector assistance to finally tourniquet this endless bleeding. Every terror attack in Kenya costs Kenya more than $1B in tourist revenue. The PMC offer was made, and Kenyatta asked President Trump for financial assistance to run this private sector solution. Trump agreed and funding was passed into law by Congress. But Team Biden took over before the already-appropriated funds were released. As a result, they were used instead on the same failed approach – the surgical decapitation strategy which has repeatedly failed globally for 20+ years. Today, Somalia still bleeds and still drains funds, while America is stuck with culturally incompatible migrants that we “cannot deport” because Somalia remains a failed state.
When does Western incompetence end?
Barack Obama, center, participates in a meeting in the White House Situation Room (2011) The Syrian Civil War saw Neocons funding a radical Sunni insurgency to depose Bashar Al Assad. This force quickly morphed into ISIS and promptly conquered half of Iraq by appealing to a Sunni population repressed by Iranian Shia proxies. The point is worth repeating. ISIS emerged directly from Neocon meddling in the Syrian Civil War. Today, in the aftermath, US forces occupy eastern Syria as some sort of ill-defined buffer between various Kurdish factions, Turkey, and the Syrian government, at a cost of billions per year and for no tangible benefit to American citizens.
Cui Bono? Who benefits? And who is benefiting from the ongoing tragedy of the war in Ukraine? Since historical perspective in conflicts is always useful, I invite readers to consider the staggering costs in manpower borne by the USSR to defeat the Wehrmacht: over 22 million lives lost compared to US losses of 250,000 troops. While the US was invading North Africa in a warm-up to the invasion of Europe, the Soviets were killing 1.2 million Axis soldiers at Stalingrad, while losing almost twice that number themselves. That loss is genetically imprinted on surviving generations, and strategically imprinted in the thinking of the Russian state.
The effect of the eastward expansion of NATO culminating in a proposal to include Ukraine despite clear red-line language expressed by the Kremlin was highly predictable. Yet the Neocons kept pressing the issue, even after assisting in the overthrow of a pro-Russian President. One should take note of how upset the US Government was when the USSR began emplacing missiles in Cuba during the early 1960s.
At the outbreak of WWII, in Britain’s greatest hour of danger, America sent them 50 surplus Navy destroyers, combat aircraft, and weaponry. Meanwhile, in the Chinese theater, combat aircraft were purchased by a Nationalist government which needed American Volunteer Group Contractor support to stop the Japanese from bombing Chinese cities. Similarly, as tensions rose in Ukraine in late 2021 and a Russian invasion looked imminent, a combination of Lend Lease and the Flying Tigers was offered to the White House. For fiscal year 2022, 200+ fully functional combat aircraft including 50 F-16s, 50 F-15s and 42 A-10s explicitly designed for destroying Soviet tanks were set to be retired, flown to the desert, and parked forever.
These are not state-of-the-art aircraft but entirely adequate when flown by well-trained contract pilots filling the gap for 18 months while Ukrainian crews could be readied. Team Biden could have made a grand announcement before the invasion stating Ukraine would never join NATO but would have the means to defend itself. This airwing deployment with weapons crews and fuel would have cost less than $800mm compared to the hundreds of billions and incalculable deaths on both sides. Announcing no NATO expansion and instant deployment of a robust air wing could have prevented the largest war in Europe in eighty years. Or did the Neocons want a war?
Which brings us to Taiwan. Taiwan, and China’s claim on it, remains the flashpoint in the ultimate cold war in the final stages of warming. Clever deterrence measures have been offered and rejected. The Pentagon wants to fight by our own playbook, but as always in war, the enemy gets a vote. A hot war between China and the USA would see US cities annihilated and a death toll in the tens of millions, at minimum. This apocalyptic carnage can only be averted by looking back through history at what has worked and what hasn’t worked in the conveyor belt of failed Washington foreign policy approaches which have dominated the last thirty years. We owe it to our children to get this right but course changes must be made immediately, before it is too late.
What we should do?
The current policy model of US security assistance is broken and counterproductive. The US military is the most expensive organization in 3,000 years of human history and has degenerated into an instrument for selling or grifting overpriced military hardware to countries that struggle to use it, let alone maintain it. The US military mows the lawn with Lamborghinis, when Kubota tractors is what our allies need.
The dozens of developing countries that suffer from narco crime, gangsterism and chaos urgently need real help. When troops are sent for advisory missions too many are sent and they don’t stay long enough to provide real assistance; while they are there they are hamstrung by lawyers into ineffectiveness.
Building lasting capability in countries takes time. Doing a three-week exercise while delivering new gifted equipment is a waste of energy and money every time. Send experienced advisors to dwell long term – for years, not months. Give advisors a path to really learn a region and culture.
The Russians are not ignorant of history and the Wagner group has stepped into the void created by US incompetence. In the Sahel and other parts of West Africa they’ve quickly become the power behind the throne. The best way to beat Wagner is to outcompete them. The same principle also applies to reforming Washington more generally. Policymakers must allow competition to flourish.
The military does not need to be so inherently governmental. If, in 1969, during the summer of Woodstock and Apollo 11, someone said that in 50 years the only way the USG would be able to get people into space would be on a SpaceX rocket, you’d be laughed out of Johnson Space Center. Before the creation of FedEx, a politician would have proclaimed government as the only entity robust enough to deliver packages overnight globally, yet today “FedEx” is a verb. It hasn’t totally replaced the US Postal Service, but it has made it run more efficiently. The same logic can be applied to the military.
The American taxpayer is paying far too much for much too little. The cozy cartel of defense contractors must be broken up, and the military made competitive again. Anti-trust enforcement and competitive tenders will stop the corruption of the thousands of lobbyists in Washington milking congress like a cow while delivering overpriced and ineffective products. The current status is unacceptable. The more consolidated the defense base, the more it behaves like the Pentagon bureaucracy: exactly what America cannot afford.
Our Founding Father’s instincts for empowering market capacities in military power are explicitly articulated in the Constitution. Before discussing “Congress shall raise a Navy” in Art 1 Sec 8 it directs Congress to mandate the private sector with a letter of Marque and Reprisal – effectively a hunting license for private contractors to interdict enemy shipping.
The litany of failures listed above supplies ample evidence that the current military status quo is ineffective. A “government-only” approach abroad is calamitous and undermines US credibility and deterrence. The foreign policy of the United States should be that our friends love us, our rivals respect us, and our enemies fear us. Instead, our friends fear our self-immolation while our rivals consume us and our enemies fire upon us without consequence.
America’s private sector has always outperformed government in solving problems. It is time to unleash America’s entrepreneurs in foreign policy to cut costs and restore American credibility. Erik D. Prince is a former Navy SEAL officer and the founder of private military company Blackwater. Among his current projects is the Unplugged phone, a privacy-focused smartphone. He can be followed @realErikDPrince.
-
 @ fe02e8ec:f07fbe0b
2025-01-22 13:05:34
@ fe02e8ec:f07fbe0b
2025-01-22 13:05:34Zum ersten Mal in der Geschichte der Menschheit …
… wissen so viele Menschen Bescheid über Propaganda. Seit ihren Anfängen etwa um 1900 bis 1920 (LeBons „Psychologie der Massen“, Bernays „Propaganda“, Lippmanns „Die öffentliche Meinung“) haben sich weltweit Tausende von Psychologen damit beschäftigt, wie Menschen beeinflusst werden können. Es existieren unzählige Websites und Bücher, in welchen die Methoden, Techniken und Tricks beschrieben werden. Jeder, der es wissen möchte, kann es wissen. Und jetzt kommt das Beste: Propaganda funktioniert nur, wenn sie nicht bemerkt wird! Nur so lange Menschen der Meinung sind, sie erhalten echte Information schenken sie ihr Glauben. Sobald sie bemerkt haben, dass verborgene Absichten dahinterstecken, sind Zweifel und Misstrauen wesentlich stärker als das Restvertrauen, das oft nur noch aus jahrelanger Gewohnheit besteht. Aber: ist Vertrauen erst verspielt lässt es sich äußerst schwer zurückgewinnen. Die Propaganda versagt. Heute (2023) glauben in Deutschland noch ca. 50% den großen Medien, in den USA sind es weniger als 20%. Propaganda verliert ihre Wirkung. Die Erzeugung einer mehrheitlich geglaubten Scheinrealität bricht zusammen.
** **
Zum ersten Mal in der Geschichte der Menschheit …
… können sich die Menschen selbstbestimmt informieren. Dank Internet, freien Medien und rührigen Einzelpersonen haben die großen Medien ihre Gatekeeper-Funktion weitgehend verloren. Während früher eine Handvoll Medienkonzerne entscheiden konnte, welche Informationen an die Menschen geliefert werden und welche nicht, ist das heute nicht mehr möglich. Jeder, der dies möchte, kann sich selbstbestimmt informieren. Damit ist die Durchsetzung einer einzig gültigen Wirklichkeitswahrnehmung seitens Politik und Medien unmöglich. Aus diesem Grund ist in den letzten Jahren der größte Zensurkomplex der Welt entstanden. Der Amerikaner Michael Shellenberger, Mitgründer von Greenpeace (mittlerweile ausgetreten) nennt es den „Censorship Industrial Complex“. Spätestens seit „Corona“ ist bekannt, wie extrem die Zensur zuschlägt, um die staatlich verordnete „Realität“ durchzusetzen. Doch je wilder die Zensur, desto offensichtlicher die Angst und Hilflosigkeit der „Narrativ Reiniger“. Doch es ist vorbei. Ist das Vertrauen verspielt so kehrt es nicht mehr zurück. Sie wissen es. Und sie wissen, dass wir es wissen. Doch sie machen weiter, denn ein Zurück ist für sie unvorstellbar. Kauft Popcorn.
Zum ersten Mal in der Geschichte der Menschheit …
… erkennen viele die Macht-Motive hinter den Weltkrisen. Der „Wertewesten“, die „regelbasierte internationale Ordnung“, Kriege, um „Demokratie und Freiheit“ zu bringen, die USA mit über 800 ausländischen Militärbasen (Russland: 9, China: 1), nie existierende Massenvernichtungswaffen, die einen Krieg rechtfertigen mussten und so weiter. Es ließe sich noch lange fortsetzen. Unzählige Historiker, aufrechte Journalisten und mutige Whistleblower haben der Welt gezeigt, worum es wirklich geht: Macht, Geostrategie, Rohstoffe, Kontrolle, Geld. Menschen, die sich unabhängig informieren, lassen sich mit den seit Jahrzehnten bekannten Phrasen nicht mehr manipulieren. Der Rückhalt für diese Politik nimmt ab, mit medialem Dauerfeuer (Ukraine, Russland, demnächst Niger?) wird versucht, gegenzusteuern. Doch weder die USA noch die Bundeswehr finden genug Rekruten für die Verteidigung der „westlichen Werte“. Ob es daran liegt, dass diese „Werte“ am Ende aussehen wie syrische Ölquellen, irakische Raffinerien oder Milliardengewinne für Rüstungskonzerne? Immer mehr der 99% erkennen, dass die 1% ohne sie zu absolut nichts Kriegerischem in der Lage wären. Und es werden monatlich mehr, die dies bemerken.
** **
Zum ersten Mal in der Geschichte der Menschheit …
… werden die großen Pläne so frühzeitig aufgedeckt. Die Bilderberger Konferenz existiert seit 1954, in der Öffentlichkeit war sie praktisch unbekannt. Obwohl dort die Creme de la Creme aus Politik, Hochfinanz, Militär, Medien, Adel und CEOs zusammenkamen, Jahr für Jahr. Doch investigative Journalisten zwangen sie dazu, eine eigene Website mit Teilnehmerlisten zu veröffentlichen. Die „Davos Clique“, das Word Economic Forum um Kissinger- und CIA-Zögling Klaus Schwab ist spätestens seit der „Pandemie“ in aller Munde. Und so weiter. All die Elite Organisationen, Think Tanks, NGOs und internationalen Institutionen stehen heute viel genauer unter Beobachtung, als dies noch vor zehn Jahren der Fall war. In den unabhängigen Medien wird frühzeitig über die Pläne berichtet, so etwa der monströse Plan der WHO, im Falle einer (gänzlich undefinierten) „Pandemiesituation“ alle Regierungen der Welt überstimmen zu können. Freie Journalisten deckten frühzeitig die (teils extremen) Unstimmigkeiten in der Corona-/ Impf-Berichterstattung auf und ermöglichten es Millionen von Menschen, selbstbestimmte Entscheidungen zu treffen. Das Beste: immer mehr Menschen sind wachsam!
** **
Zum ersten Mal in der Geschichte der Menschheit …
… können sich Millionen von Menschen frei vernetzen. Whatsapp, telegram, Signal: mehr als drei Milliarden Menschen auf der ganzen Welt können sich heute miteinander verbinden, kommunizieren, Informationen austauschen. Vielleicht ist dies sogar die größte Neuerung von allen, denn damit sind Dinge möglich, die früher undenkbar waren. Videos, die innerhalb eines Tages millionenfach gesehen werden und üble Machenschaften aufdecken. Gruppen, die auf mehrere 100.000 Mitglieder anwachsen und sich verabreden können. Podcaster wie Joe Rogan oder Tucker Carlson, von denen jeder mehr Zuhörer erreicht als alle Hauptnachrichtensender der USA zusammen! Deshalb ja auch die massiven Versuche von Regierungen und Geheimdiensten, die Verschlüsselungen der Plattformen zu brechen. Es ist dasselbe wie mit der Zensur: Angst und Hilflosigkeit lassen sie über alle Stränge schlagen. Wir werden sehen, wie weit sie bereit sind zu gehen.
** **
Zum ersten Mal in der Geschichte der Menschheit …
… ist die Bewusstseinsentwicklung so weit fortgeschritten. Mit der „68er-Generation“ begann mehr als nur Flower Power, Rock und psychedelische Drogen. Es begann eine Generation sich mit ihrer eigenen Innenseite zu beschäftigen. Für die östlichen Religionen nichts Neues, im Gegenteil, es ist deren Schwerpunkt. Doch in den Ländern des ungebremsten Wirtschaftswachstums war das bewusste Erleben der eigenen Innenwelt etwas ziemlich Neues. Meditation, bewusstseinserweiternde Substanzen (Entheogene), Psychologie im Alltag und eine Reihe spiritueller und esoterischer Ansätze eröffneten eine vollkommen neue Welt. Heute können wir offen über Traumatisierungen, Meditations-Erfahrungen, Non-duale Zustände, epigenetische Weitergabe generationaler Themen, systemische Erfahrungen und mehr reden. Themen, die der Generation der vor 1950 Geborenen nur in sehr ausgewählten Kreisen zugänglich waren. Wir können Meta-Perspektiven einnehmen, uns selbst beobachten, uns als Teil des Ganzen begreifen und noch viel mehr. Denn das ist erst der Anfang!
Zum ersten Mal in der Geschichte der Menschheit …
… werden Verstand, Herz und GEIST integral gesehen. Entgegen der derzeit weit verbreiteten Ansicht, dass die KIs und der Transhumanismus uns alle zu unnützen Essern reduzieren werden steht die Auffassung, dass wir weit mehr sind als rein materielle Gebilde. Auch wenn dies heute (noch) nicht unwiderlegbar zu beweisen ist, so zeigen doch Millionen von Erfahrungsberichten, dass Bewusstsein eine komplett andere Dimension darstellt als die Atome, aus denen unser Gehirn besteht. Unser Verstand ist das Werkzeug, mit dem wir den Alltag bewältigen. Unser Herz – im übertragenen Sinne – ist unser emotionales und Bindungszentrum. Unser GEIST ist das, was über uns hinausweist. Und möglicherweise schon vor diesem materiellen Körper existiert hat – und weiterexistieren wird. Klar handelt es sich hier um sehr persönliche Fragen, doch zumindest leben wir in einer Zeit, in der all dies einen Platz hat und erlebt, gespürt und diskutiert werden kann. Und das unterscheidet diese Zeit fundamental von den letzten 2000 Jahren. Danke dafür.
** **
Zum ersten Mal in der Geschichte der Menschheit …
… braucht es keinen großen Führer, um Großes zu erreichen. Das ist Spekulation. Denn auch wenn alles hier Beschriebene richtig wäre, so lässt sich diese Aussage nicht beweisen. Im Gegenteil, es sieht eher danach aus, dass die Masse noch immer nicht in der Lage ist, sich selbst zu organisieren. Nicht einmal in kleinen Gruppen von 20, 50 oder 100 Personen. Eine Vielzahl gescheiterter Projekte spricht Bände. Zugleich sind auch einige der engagierten Personen aus der freiheitlichen Bewegung nicht frei von Narzissmus und verhindern teilweise eine übergreifende Zusammenarbeit. Dennoch: auch wenn sich der Weg erst schemenhaft zeigt, die Richtung ist klar: vernetzte Zellen mit hoher Autonomie. Es wird viele Modelle geben, viele Versuche, manches wird scheitern und anderes wird gelingen. Denn eines ist sicher: auf den „Großen Anführer“ wird hier keiner mehr warten!
** **
Zum ersten Mal in der Geschichte der Menschheit …
… nimmt uns keiner die Verantwortung ab. Das kann man positiv oder negativ sehen. Denn es bedeutet zweifellos, dass noch viel mehr Menschen erst ihre persönliche Heldenreise auf dem Weg des Erwachsenwerdens, der Selbstverantwortung, durchlaufen und durchleiden müssen. There is no free lunch. Wer auf den paternalistischen Staat, Grundeinkommen oder ewige Versorgung setzt, der hat nicht verstanden, wohin die Reise geht. Macht nichts, denn immer ist es eine Minderheit, die vorangeht. Die Pioniere, Abenteurer, Entdecker, die heute keine neuen Kontinente mehr bereisen, sondern neue Formen des Zusammenlebens und -arbeitens entdecken. Dahin fährt der Zug, ein paar sitzen ganz klar vorne, ein paar sorgen für Treibstoff und die Versorgung und viele fahren neugierig mit. Und das ist auch gut so. Denn weiter sind wir in unserer Evolution noch nicht. Aber wir haben ja noch ein paar Tausend Jahre vor uns. Was wir heute üben und kultivieren dürfen, das ist persönlicher Mut, der es uns immer öfter gestattet, aus Konformität und Autoritätshörigkeit auszubrechen!
** **
Zum ersten Mal leben wir in dieser Zeit!
Erstveröffentlichung bei "Der Sandwirt"
-
 @ 7ed5bd1c:4caa7587
2025-01-22 11:32:45
@ 7ed5bd1c:4caa7587
2025-01-22 11:32:45เครือข่ายที่เติบโต: ทำไมเครือข่าย Bitcoin ถึงมีคุณค่ามากขึ้นเรื่อย ๆ?
ในโลกของเทคโนโลยีและเครือข่าย Bitcoin การเติบโตของจำนวนผู้ใช้งานไม่เพียงแค่ส่งผลต่อการใช้งาน แต่ยังเพิ่มมูลค่าให้กับเครือข่ายเองด้วย หลักการนี้สามารถอธิบายได้ผ่าน "Metcalfe’s Law" ที่กล่าวว่า มูลค่าของเครือข่ายหนึ่ง ๆ เพิ่มขึ้นตามกำลังสองของจำนวนผู้ใช้งาน
Metcalfe’s Law และ Bitcoin
Metcalfe’s Law เป็นกุญแจสำคัญในการอธิบายว่าทำไมเครือข่าย Bitcoin ถึงมีมูลค่าเพิ่มขึ้นตามจำนวนผู้ใช้งาน โดยกฎนี้กล่าวว่า:
มูลค่าของเครือข่าย = จำนวนผู้ใช้งาน^2
นั่นหมายความว่า หากจำนวนผู้ใช้งาน Bitcoin เพิ่มขึ้นเพียง 2 เท่า มูลค่าของเครือข่ายอาจเพิ่มขึ้นถึง 4 เท่า
การเติบโตของเครือข่าย Bitcoin
-
ผู้ใช้งานเพิ่มขึ้นอย่างต่อเนื่อง: ปัจจุบัน Bitcoin มีผู้ใช้งานหลายล้านคนทั่วโลก และยังคงมีแนวโน้มเติบโตเมื่อคนหันมาให้ความสนใจเกี่ยวกับการเก็บมูลค่าและการปกป้องทรัพย์สิน
-
การยอมรับที่กว้างขึ้น: บริษัทและธุรกิจจำนวนมากเริ่มยอมรับ Bitcoin เป็นวิธีการชำระเงิน เช่น Tesla, PayPal และบริษัทใหญ่ ๆ ทั่วโลก
-
การสนับสนุนจากสถาบันการเงิน: นักลงทุนสถาบันและธนาคารบางแห่งเริ่มเข้ามามีส่วนร่วมกับ Bitcoin มากขึ้น ซึ่งช่วยเสริมสร้างความน่าเชื่อถือและความต้องการในตลาด
ผลกระทบต่อมูลค่าเครือข่าย
-
สภาพคล่องที่เพิ่มขึ้น: เมื่อมีผู้ใช้งานมากขึ้น การซื้อขาย Bitcoin ก็เพิ่มขึ้น ส่งผลให้ตลาดมีสภาพคล่องสูงขึ้นและการเคลื่อนไหวของราคามีเสถียรภาพ
-
มูลค่าที่มั่นคงในระยะยาว: การเติบโตของเครือข่ายช่วยเสริมความเชื่อมั่นและลดความเสี่ยงที่ Bitcoin จะกลายเป็นเทคโนโลยีล้มเหลว
-
การกระจายอำนาจที่ดียิ่งขึ้น: จำนวนผู้ใช้งานที่เพิ่มขึ้นทำให้ Bitcoin เป็นเครือข่ายที่ยากต่อการควบคุมจากศูนย์กลาง
Bitcoin กับการเติบโตอย่างยั่งยืน
การเติบโตของเครือข่าย Bitcoin ไม่ได้เป็นเพียงแค่การเพิ่มจำนวนผู้ใช้งาน แต่ยังสะท้อนถึงการยอมรับที่เพิ่มขึ้นในฐานะทรัพย์สินดิจิทัลที่มีคุณค่าและศักยภาพในการปฏิวัติระบบการเงินดั้งเดิม แล้วคุณล่ะ เห็นการเติบโตของ Bitcoin เป็นโอกาสหรือความท้าทาย? แสดงความคิดเห็นของคุณด้านล่าง!
-
-
 @ b17fccdf:b7211155
2025-01-22 10:39:19
@ b17fccdf:b7211155
2025-01-22 10:39:19What's changed
- New bonus guide dedicated to install/upgrade/uninstall PostgreSQL
- Modified the LND guide to use PostgreSQL instead of bbolt
- Modified the Nostr relay guide to use PostgreSQL instead of SQLite (experimental)
- Modified the BTCPay Server bonus guide according to these changes
- Used the lndinit MiniBolt organization fork, to add an extra section to migrate an existing LND bbolt database to PostgreSQL (🚨⚠️Experimental - use it behind your responsibility⚠️🚨)
- New Golang bonus guide as a common language for the lndinit compilation
- Updated LND to v0.18
- New Bitcoin Core extra section to renovate Tor & I2P addresses
- New Bitcoin Core extra section to generate a full
bitcoin.conffile - Rebuilt some homepage sections and general structure
- Deleted the
$symbol of the commands to easy copy-paste to the terminal - Deleted the initial incoming and the outgoing rules configuration of UFW, due to it being by default
🪧 PD: If you want to use the old database backend of the LND or Nostr relay, follow the next extra sections:
- Use the default bbolt database backend for the LND
- Use the default SQLite database backend for the Nostr relay
⚠️Attention⚠️: The migration process was tested on testnet mode from an existing bbolt database backend to a new PostgreSQL database using lndinit and the results were successful. However, It wasn't tested on mainnet, according to the developer, it is in experimental status which could damage your existing LND database.🚨 Use it behind your responsibility 🧼
🔧 PR related: https://github.com/minibolt-guide/minibolt/pull/93
♻️ Migrate the PostgreSQL database location
Attention!! These instructions are invalid since the latest changes applied to the PostgreSQL bonus guide. See more information on the recent associated post by clicking ~ > HERE < ~
If you installed NBXplorer + BTCPay Server before 05/06/2024, it is probably you have the database of the PostgreSQL cluster on the default path (
/var/lib/postgresql/16/main/), follow the next instructions to migrate it to the new dedicated location on/data/postgresdbfolder:- With user
admincreate the dedicated PostgreSQL data folder
sudo mkdir /data/postgresdb- Assign as the owner to the
postgresuser
sudo chown postgres:postgres /data/postgresdb- Assign permissions of the data folder only to the
postgresuser
sudo chmod -R 700 /data/postgresdb- Stop NBXplorer and BTCPay Server
sudo systemctl stop nbxplorer && sudo systemctl stop btcpayserver- Stop PostgreSQL
sudo systemctl stop postgresql- Use the rsync command to copy all files from the existing database on (
/var/lib/postgresql/16/main) to the new destination directory (/data/postgresdb)
sudo rsync -av /var/lib/postgresql/16/main/ /data/postgresdb/Expected output:
``` sending incremental file list ./ PG_VERSION postgresql.auto.conf postmaster.opts postmaster.pid base/ base/1/ base/1/112 base/1/113 base/1/1247 base/1/1247_fsm base/1/1247_vm base/1/1249 base/1/1249_fsm base/1/1249_vm [...] pg_wal/000000010000000000000009 pg_wal/archive_status/ pg_xact/ pg_xact/0000
sent 164,483,875 bytes received 42,341 bytes 36,561,381.33 bytes/sec total size is 164,311,368 speedup is 1.00 ```
- Edit the PostgreSQL data directory on configuration, to redirect the store to the new location
sudo nano /etc/postgresql/16/main/postgresql.conf --linenumbers- Replace the line 42 to this. Save and exit
data_directory = '/data/postgresdb'- Start PostgreSQL to apply changes and monitor the correct status of the main instance and sub-instance monitoring sessions before
sudo systemctl start postgresql- You can monitor the PostgreSQL main instance by the systemd journal and check the log output to ensure all is correct. You can exit the monitoring at any time with Ctrl-C
journalctl -fu postgresqlExample of the expected output:
Nov 08 11:51:10 minibolt systemd[1]: Stopped PostgreSQL RDBMS. Nov 08 11:51:10 minibolt systemd[1]: Stopping PostgreSQL RDBMS... Nov 08 11:51:13 minibolt systemd[1]: Starting PostgreSQL RDBMS... Nov 08 11:51:13 minibolt systemd[1]: Finished PostgreSQL RDBMS.- You can monitor the PostgreSQL sub-instance by the systemd journal and check log output to ensure all is correct. You can exit monitoring at any time with Ctrl-C
journalctl -fu postgresql@16-mainExample of the expected output:
Nov 08 11:51:10 minibolt systemd[1]: Stopping PostgreSQL Cluster 16-main... Nov 08 11:51:11 minibolt systemd[1]: postgresql@16-main.service: Succeeded. Nov 08 11:51:11 minibolt systemd[1]: Stopped PostgreSQL Cluster 16-main. Nov 08 11:51:11 minibolt systemd[1]: postgresql@16-main.service: Consumed 1h 10min 8.677s CPU time. Nov 08 11:51:11 minibolt systemd[1]: Starting PostgreSQL Cluster 16-main... Nov 08 11:51:13 minibolt systemd[1]: Started PostgreSQL Cluster 16-main.- Start NBXplorer and BTCPay Server again
sudo systemctl start nbxplorer && sudo systemctl start btcpayserver- Monitor to make sure everything is as you left it. You can exit monitoring at any time by pressing Ctrl+C
journalctl -fu nbxplorer
journalctl -fu btcpayserver
Enjoy it MiniBolter! 💙
-
 @ fbf0e434:e1be6a39
2025-01-22 09:54:27
@ fbf0e434:e1be6a39
2025-01-22 09:54:27Hackathon 概要
台北区块链周的年度黑客松 Taipei Blockchain Week 2024 - Hackathon 圆满结束,共收到223个项目提交,吸引了475名开发者参与。活动历时一个多月,于2024年12月12日至14日通过线上和线下报名结合的方式进行。活动的主题“Onboard”聚焦于推进Web3技术的采用,突出Solana、Ethereum和Bitcoin等生态系统中的创新。
参与者参与了各种活动,包括workshops和demo day,展示他们的项目并与行业专家、创始人和风险投资家互动。这种混合形式旨在提升项目质量和提供更多的社交机会。
组织者报告称,有500位精选的开发者参与其中,通过Discord和Telegram访问详细的赏金和社区连结。Hackathon 强调其在将台湾建立为区块链创新中心方面的作用,这与Taipei Blockchain Week的总体目标一致。它还突出了台湾的战略重要性、文化多样性和技术能力,同时强调了其安全和良好的国际会议环境。
Hackathon 获奖者
Avalanche 奖项获奖者
- Avax Blinks - 通过可共享链接简化Avalanche上的链上交易,用于支付和NFT购买。项目使用Next.js构建,强调移动优先的设计并增强社交媒体上的DeFi互动。
- Ava the Portfolio Managing Agent - 使用AI进行策略优化,管理Avalanche上的DeFi组合。该解决方案利用Next.js、TypeScript和Avalanche区块链进行全面管理。
0G 奖项获奖者
- echoX - 去中心化的AI驱动交易聚合器,利用0G的Service Marketplace简化加密资产管理,专注于透明性和流动性聚合。
- DeCentraChat - 提供带有安全区块链存储的去中心化AI模型推理,使用Solidity和像Wagmi、Next.js这样的框架开发,提供强大的平台交互。
SOON 奖项获奖者
- Memecoooins - 通过包含meme coins的神秘钱包简化加密投资,集成了SvelteKit、Solana和Raydium用于安全管理和交易。
- BasketFi - 管理Solana上的代币篮子,支持无缝的交换和性能跟踪,并通过Jupiter和Solana的扩展功能进行集成。
Zero Computing 奖项获奖者
- Ikkyu - 通过Solana上的游戏化互动转变meme coins,利用ZKWASM和社区参与通过移动活动推广文化运动。
- Yaminogemu - 使用BONK代币进行Solana上的GameFi和DeFi互动,通过无服务器架构提供安全的竞争和收入机会。
BNB Chain 奖项获奖者
- BNB-Voice - 在BNB Chain上提供基于区块链的开票,集成了Request Network以增强透明度,便于安全开票和分析。
- Income Trust - 一个去中心化的信托基金,在Binance Smart Chain上进行收益管理,集成DeFi以及通过OpenZeppelin保证安全和灵活提款。
Delphinus Labs 奖项获奖者
- zkGuess - 在数字猜谜游戏中使用ZKWasm技术,强调Web3集成和区块链环境中的直观用户互动。
Genopets 奖项获奖者
- SolGame - 在Solana上实施赚取模式的地牢游戏,利用Metaplex NFT Marketplace Protocol进行去中心化的游戏奖励。
欲了解有关所有项目的更多详情,请访问DoraHacks。
关于组织者
台北区块链周 Taipei Blockchain Week
TBW是亚洲区块链领域的重要活动组织者。继上届活动成功活动吸引了超过2,000名与会者后,组织方将于12月11日至16日举办Taipei Blockchain Week 2023,预计将吸引超过5,000名参与者。活动旨在构建、连接和扩大区块链社群,重申促进行业增长和合作的承诺。凭借在区块链环境中的强大影响力,Taipei Blockchain Week 继续推广增强技术发展和采用的倡议和项目。
-
 @ da0b9bc3:4e30a4a9
2025-01-22 09:38:20
@ da0b9bc3:4e30a4a9
2025-01-22 09:38:20Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/859749
-
 @ ed84ce10:cccf4c2a
2025-01-22 09:26:21
@ ed84ce10:cccf4c2a
2025-01-22 09:26:21Hackathon Summary
The Taipei Blockchain Week 2024 - Hackathon concluded successfully, featuring 223 project submissions and participation from 475 developers. The event ran for over a month, culminating in both virtual and in-person sessions held from December 12 to 14, 2024. The central theme, "Onboard," emphasized advancing Web3 technology adoption, highlighting innovations within ecosystems such as Solana, Ethereum, and Bitcoin.
Participants engaged in various activities, including workshops and a demo day, which enabled them to showcase their projects and interact with industry experts, founders, and venture capitalists. The hybrid format intended to enhance project quality and networking opportunities.
Organizers reported that 500 selected builders participated, accessing detailed bounties and community connections via Discord and Telegram. The hackathon emphasized its role in establishing Taiwan as a hub for blockchain innovation, aligning with the broader objectives of Taipei Blockchain Week. It also underscored Taiwan's strategic importance, cultural diversity, and technological capacity, while highlighting its secure and well-connected environment for conferences and international collaboration.
Hackathon Winners
Avalanche Prize Winners
- Avax Blinks - Simplifies on-chain transactions on Avalanche through shareable links for payments and NFT purchases. Built with Next.js, the project emphasizes mobile-first design and enhances DeFi interactions on social media.
- Ava the Portfolio Managing Agent - Manages DeFi portfolios on Avalanche using AI for strategy optimization. The solution utilizes Next.js, TypeScript, and the Avalanche blockchain for comprehensive management.
0G Prize Winners
- echoX - A decentralized AI-driven trading aggregator that streamlines crypto management using 0G’s Service Marketplace, focusing on transparency and liquidity aggregation.
- DeCentraChat - Provides decentralized AI model inferences with secure blockchain storage, developed using Solidity and frameworks such as Wagmi and Next.js for robust platform interaction.
SOON Prize Winners
- Memecoooins - Simplifies crypto investments through mystery wallets containing meme coins, integrating SvelteKit, Solana, and Raydium for secure management and transactions.
- BasketFi - Manages token baskets on Solana, allowing seamless swaps and performance tracking, with integration from Jupiter and Solana's scalability features.
Zero Computing Prize Winners
- Ikkyu - Transforms meme coins through gamified interactions on Solana, employing ZKWASM and community engagement to promote cultural movements via mobile activities.
- Yaminogemu - Uses BONK tokens for GameFi and DeFi engagements on Solana, providing secure competition and income opportunities through a serverless architecture.
BNB Chain Prize Winners
- BNB-Voice - Offers blockchain-based invoicing on the BNB Chain, facilitating secure invoicing and analytics with Request Network integration for enhanced transparency.
- Income Trust - A decentralized trust fund on Binance Smart Chain, integrating DeFi for yield management with OpenZeppelin for security and flexible withdrawals.
Delphinus Labs Prize Winners
- zkGuess - Utilizes ZKWasm technology in a number-guessing game that emphasizes Web3 integration and intuitive user engagement within blockchain environments.
Genopets Prize Winners
- SolGame - A dungeon game on Solana implementing Play-to-Earn models, leveraging the Metaplex NFT Marketplace Protocol for decentralized gaming rewards.
For more details on all projects, visit DoraHacks.
About the Organizer
Taipei Blockchain Week
Taipei Blockchain Week is a significant event organizer in the blockchain sector. Following a previous successful event, which attracted over 2,000 attendees, the organization is hosting Taipei Blockchain Week 2023 from December 11-16, expecting more than 5,000 participants. The event aims to build, connect, and scale within the blockchain community, underscoring a commitment to fostering growth and collaboration in the industry. With a strong presence in the blockchain environment, Taipei Blockchain Week continues to promote initiatives and projects that enhance technological development and adoption.
-
 @ 16d11430:61640947
2025-01-22 09:05:35
@ 16d11430:61640947
2025-01-22 09:05:35Programming, once considered a niche skill, is now integral to the infrastructure of modern economies. However, as the pace of technological advancement accelerates, programmers face a unique and precarious psychosocial environment. Their profession is not only defined by its intellectual demands but also by its vulnerability to rapid obsolescence, economic shifts, and increasingly volatile employment trends.
This article explores how Bitcoin and blockchain technology provide a critical safety net for programmers in this environment, while examining the trends that are shaping their lives and livelihoods.
The Fragility of the Programming Skillset
Programming is an inherently ephemeral skill. Languages, frameworks, and tools evolve rapidly, demanding continuous learning. This perpetual race can result in high levels of stress and burnout, especially when coupled with:
-
Job Insecurity: Policy changes, corporate restructuring, and global economic downturns can lead to sudden layoffs. For programmers, a brief hiatus from work can lead to skills becoming outdated.
-
Time Scarcity: The intense focus required in programming often leaves little room for socialization and personal development, compounding feelings of isolation.
-
Hyper-competitiveness: The global talent pool means programmers are not only competing locally but also against peers from lower-cost regions.
The Role of Bitcoin and Blockchain in Programmer Resilience
Blockchain technology, particularly Bitcoin, addresses several of the systemic vulnerabilities faced by programmers:
-
Direct Payments Without Intermediaries Platforms like the Lightning Network enable programmers to receive instant, borderless payments for freelance or contract work. This eliminates reliance on centralized payment processors, which can block funds or impose high fees.
-
Immutable Portfolios Blockchain technology can serve as a tamper-proof ledger for showcasing work and contributions. For example, Gitcoin uses blockchain to validate open-source contributions, providing a secure and transparent record of a programmer's expertise.
-
Decentralized Infrastructure With tools like smart contracts, programmers can set up automated agreements, ensuring they are paid for milestones reached. This reduces the risks of non-payment or contract disputes.
Emerging Trends and Supporting Evidence
-
Layoffs and Economic Downturns In 2023, mass layoffs at major tech firms, including Meta, Amazon, and Google, highlighted the fragility of even the most skilled workers in traditional employment models. Layoff Tracker provides real-time data on these layoffs.
-
The Rise of Freelance Platforms Freelance platforms such as Upwork and Toptal report a growing trend in programmers seeking gig work instead of full-time employment. Freelancer Study 2023 highlights that more professionals are choosing freelancing for autonomy and diversification.
-
Blockchain Adoption in Payments The rise of platforms like OpenBazaar and Stacks demonstrates an increasing number of professionals using blockchain for direct payments and decentralized marketplaces. Bitcoin Usage Trends showcases how micropayments are growing in popularity for digital work.
-
Mental Health Challenges Reports from the World Health Organization indicate that tech professionals experience higher rates of anxiety and burnout than other professions. WHO Study on Burnout underscores the urgent need for systemic change.
The Path Forward
To mitigate the psychosocial challenges programmers face, the following steps are essential:
-
Adopt Blockchain for Payments and Portfolios By integrating blockchain into their professional lives, programmers can ensure transparency, security, and autonomy.
-
Foster Community and Collaboration Decentralized networks like Stack Overflow and GitHub are critical for collaboration and peer support.
-
Upskilling and Adaptability Lifelong learning must be embraced, but organizations should also invest in reskilling programs to retain talent.
-
Advocate for Policy Changes Governments and industry bodies must address the precarity of tech work through better labor protections and decentralized economic models.
Conclusion
As technology continues to reshape industries, programmers find themselves at the epicenter of change—but not without challenges. The ephemerality of their skills, coupled with the demands of their work, places them in a uniquely vulnerable position. However, the rise of Bitcoin and blockchain technology offers a lifeline by enabling autonomy, security, and resilience in an otherwise unstable environment.
By embracing decentralized infrastructure, programmers can not only weather the current challenges but also help build a more equitable and sustainable future.
-
-
 @ c8adf82a:7265ee75
2025-01-22 08:41:21
@ c8adf82a:7265ee75
2025-01-22 08:41:21I have Asperger’s
I see life like a game
I am super competitive
I min max my life
I am curious
I am hardworking
I am both scientist and engineer
I rank global in most strategy games
I was a pure atheist
I had a thought to kill God
I have been fat and fit
I have been set up to jail
I have been rich and poor and wealthy
I am recovering from nerve damage
I have everything that I want
I felt most things a human can feel
I don’t want recognition
I can’t force you to listen
I am purely doing this for the world
I want you all to know
I tried to prove the Bible wrong
I am humbled beyond belief
I am now a servant of Christ
-
 @ ae6ce958:d0f02c7d
2025-01-22 07:18:07
@ ae6ce958:d0f02c7d
2025-01-22 07:18:07The digital transformation landscape has witnessed groundbreaking shifts with the adoption of blockchain technologies. Among these, DamageBDD stands out as a pioneering tool for behavior-driven development (BDD) enhanced by blockchain integration. By leveraging the Aeternity Name Service (AENS), DamageBDD.chain offers a decentralized and user-friendly way to access DamageBDD services, ensuring unprecedented decentralization and liquidity availability.
As part of our vision, DamageBDD is preparing to integrate with the decentralized app (dApp) ecosystem, extending its functionality and enabling developers to build directly on top of DamageBDD’s blockchain-based verification tools.
What is Aeternity AENS?
The Aeternity Name Service (AENS) is a naming system that allows for the creation of human-readable, blockchain-secured addresses. Similar to how DNS simplifies access to websites, AENS maps complex blockchain addresses or smart contracts to easy-to-remember names, such as DamageBDD.chain. This service not only enhances user experience but also aligns with the ethos of decentralization by removing centralized gatekeepers.
Why DamageBDD.chain?
- Decentralized Access
By hosting DamageBDD services under the DamageBDD.chain AENS domain, users bypass centralized intermediaries. All interactions, from accessing documentation to executing verification and payment processes, occur directly on the blockchain.
- Seamless User Experience
Remembering complex wallet or contract addresses can be cumbersome. With DamageBDD.chain, users can easily navigate and utilize the platform using a straightforward name, ensuring accessibility even for non-technical stakeholders.
- Enhanced Liquidity
Through DamageBDD’s integration with Aeternity's blockchain and AENS, liquidity is always available. This is because the system leverages Aeternity’s native AE tokens and compatible decentralized exchanges, ensuring a smooth flow of resources for project funding and payouts.
- Immutable Verification
DamageBDD is built on the premise of immutable verification of behavior-driven development tests. By anchoring this on Aeternity and accessing it via DamageBDD.chain, every test, milestone, and payout is transparently recorded and verifiable on-chain.
Expanding into the dApp Ecosystem
To further enhance its utility, DamageBDD is actively developing plans to integrate with the broader decentralized app (dApp) ecosystem. This evolution will allow developers to build and deploy dApps that leverage DamageBDD’s blockchain-based verification capabilities. Key benefits include:
-
Programmable Verification: Developers will be able to programmatically trigger BDD test verifications within their own dApps, creating a seamless workflow for quality assurance.
-
Custom dApp Integrations: Businesses can integrate DamageBDD into their decentralized applications for domain-specific use cases, such as supply chain validation, financial reporting, or compliance tracking.
-
On-Chain API Services: DamageBDD will expose on-chain APIs accessible via DamageBDD.chain, enabling dApps to interact directly with the platform for verification and payout processes.
-
Tokenized Incentives for Testing: With integration into dApps, organizations can incentivize contributors by offering tokenized rewards for successfully passing test cases and milestones.
How It Works
- Registration on AENS
The DamageBDD.chain domain was registered using Aeternity's AENS protocol. This domain is tied to the DamageBDD smart contracts and associated services.
- Accessing the Platform
Users input DamageBDD.chain in their Aeternity-compatible wallets or applications (e.g., Superhero.com) to interact with the platform. The AENS resolves the human-readable name to the corresponding smart contract address.
- Executing Transactions
Developers can perform BDD-related actions such as verifying test cases, executing payouts, or accessing analytics directly through blockchain interactions tied to the DamageBDD smart contracts.
- dApp Integration
Once integrated into the dApp ecosystem, DamageBDD will allow decentralized applications to call its services via DamageBDD.chain, automating testing and verification for diverse workflows.
- Ensuring Liquidity
The platform uses AE tokens for operations, enabling instant liquidity through decentralized exchanges. Users can also integrate Bitcoin payments via the Lightning Network for added flexibility.
Implications for the Future
The integration of DamageBDD with the Aeternity AENS system is more than a technical enhancement; it’s a paradigm shift in how blockchain-based BDD solutions are accessed and utilized. With plans to expand into the dApp ecosystem, DamageBDD will become an indispensable tool for decentralized projects, offering seamless, secure, and programmable BDD services.
Imagine a future where dApps across industries—from healthcare to finance—can automate behavior-driven testing, ensure compliance, and transparently reward contributors, all anchored to the immutable blockchain.
Conclusion
DamageBDD’s integration with the Aeternity AENS system underscores its commitment to decentralization and usability. By leveraging DamageBDD.chain, developers, testers, and enterprises gain secure, transparent, and decentralized access to a cutting-edge BDD platform. Coupled with instant liquidity availability, future dApp integrations, and immutable blockchain records, this approach positions DamageBDD as a leader in decentralized behavior-driven development.
To experience the next evolution of BDD and decentralized application integration, look no further than DamageBDD.chain—where decentralization meets development excellence.
-
 @ 16d11430:61640947
2025-01-22 05:42:45
@ 16d11430:61640947
2025-01-22 05:42:45Banking has long been an essential pillar of modern life, serving as the gatekeeper for our financial transactions. Yet, when we step back and analyze the processes and systems that underpin our interactions with banks, a recurring theme emerges—deflection and subterfuge. This is especially apparent in cross-border transactions, where complexity and fear of non-compliance often overshadow the simplicity of what should be a straightforward process.
A Personal Story of Complexity
Imagine needing to transfer money from an account in one country to another. You are told that the funds are in your NRO (Non-Resident Ordinary) account, which has specific tax implications for outward remittances. Suddenly, the bank introduces additional requirements: a tax clearance certificate, a digital signature, and consultation with a Chartered Accountant (CA). These demands, often presented piecemeal, turn what should be a simple transfer into a bureaucratic maze.
In this scenario, the bank is not denying your ability to transfer funds outright but instead uses a series of layered requirements to delay the process. Along the way, it fosters anxiety with warnings about penalties for non-compliance and risks to data security. For instance, suggesting that digital signatures “may not be safe” subtly undermines confidence in what should be a straightforward solution.
The Tools of Deflection
Banks employ several techniques to maintain control over financial transactions:
-
Partial Disclosure Often, the full scope of requirements is not revealed upfront. You may only learn of additional steps—such as tax forms (Form 15CA and 15CB)—after you’ve started the process. This approach creates dependency on the bank’s guidance and slows down the process.
-
Fear-Mongering Phrases like “tax implications,” “compliance issues,” and “serious complications” are used to emphasize potential risks, placing the emotional burden on the customer. Even when the risks are manageable, the language makes the process seem daunting and urgent.
-
Complexity by Design Repatriating funds from an NRO account requires a tax clearance certificate, which in turn involves engaging a CA and obtaining a digital signature. Each step adds cost, time, and friction, discouraging customers from completing their transactions.
-
Shifting Responsibility While the bank positions itself as a neutral enforcer of regulations, it shifts the burden of compliance entirely onto the customer. In the case of NRO accounts, this includes not only navigating complex tax laws but also securing external services to meet the bank’s requirements.
The Broader Implications
This dynamic is not just about one transaction—it reflects a broader systemic issue in how banks and financial institutions operate. By creating and maintaining complexity, banks ensure their centrality in financial systems. Every added layer of compliance generates revenue for intermediaries, from CAs to agencies offering digital signature services.
At its core, this approach consolidates control, discouraging people from questioning the system while creating dependency on institutions to navigate it.
A Stark Contrast: Decentralized Alternatives
Contrast this with decentralized systems like Bitcoin, where transactions are transparent, direct, and free from intermediaries. In decentralized finance, complexity is replaced with clarity: the rules are encoded, and the system operates without fear-mongering or hidden requirements.
While decentralized systems are not without their challenges, they highlight how much of the friction in traditional banking is artificial, designed to maintain control rather than provide true utility.
Moving Forward: Empowering the Individual
To navigate these challenges, customers must take an active role in understanding their rights and responsibilities:
-
Seek Clarity: Always insist on full, written disclosure of requirements upfront.
-
Be Informed: Familiarize yourself with relevant regulations, such as the RBI guidelines for repatriation of funds from NRO accounts.
-
Streamline Processes: Explore authorized solutions for digital signatures and tax compliance independently, avoiding unnecessary intermediaries.
-
Escalate When Necessary: If a bank creates undue delays or friction, consider escalating the issue to regulatory bodies like the RBI Ombudsman.
Conclusion
Banks operate within a system that thrives on opacity and control, using deflection and subterfuge to create dependency. However, by understanding the tools they use and asserting your rights, you can navigate these systems more effectively.
The ultimate goal should be financial systems that are transparent, straightforward, and customer-centric—whether that’s through reforming traditional banks or embracing decentralized alternatives. Until then, it’s essential to recognize and address the subtle dynamics that keep customers in the dark.
-
-
 @ 00eba731:09746909
2025-01-22 05:20:24
@ 00eba731:09746909
2025-01-22 05:20:24Managing risks is crucial for business success, as it helps protect operations and ensure stability in uncertain situations. This infographic provides an overview of effective risk management strategies, including identifying potential risks, assessing their impact, and implementing measures to mitigate them, helping businesses stay resilient and prepared.
-
 @ 5adb967d:ac1f7d04
2025-01-22 03:41:12
@ 5adb967d:ac1f7d04
2025-01-22 03:41:12In this information age, radio communication has penetrated into every aspect of life. Whether it is government affairs, military, business, or personal privacy, may be subject to eavesdropping and radio wave harassment. In the face of this grim reality, how to build an impenetrable line of defense for the key confidential communications, has become an extremely urgent issue. Communication shielding, is to effectively block eavesdropping interference, to ensure absolute communication security of the magic weapon.
Communication shielding protection principle, is the use of masking performance of electromagnetic rf jammer materials, in the device around the formation of a “static area”. Into this special space, any radio wave signals will be completely blocked out, can not penetrate them. Whether it is the most advanced passive eavesdropping equipment, or intentional harassment of active electromagnetic interference, in this invulnerable “static area” in front of, all will be completely off, out of action.
In fact, electromagnetic shielding technology has long been popular in the military field. The core components of countless advanced weapons and equipment, are closely protected by this material to ensure that the key system from the outside world interference. Some special places also widely used fixed shielding facilities, to create an absolutely reliable quiet environment.
However, today, mobile offices and field operations are becoming more and more common, and the traditional fixed shielding facilities are difficult to meet the flexible deployment requirements. Therefore, portable communication shielding has emerged as the best on-site confidentiality protection tool.
Simply press the power button, most portable shielding can be immediately effective. Their powerful electromagnetic recording jammer ability, enough to form a “static area radius” within a few meters to dozens of meters in the surrounding area. As long as you enter, no matter what kind of unauthorized eavesdropping equipment, radio interference sources, all will be hard “static zone barrier” intercepted.
Users in this safe space, you can carry out all kinds of confidential calls, video conferencing or secret work, absolutely foolproof, free from any prying eyes and harassment. At the same time, another great use of the shield is to prevent the leakage of radio signals and loss of confidentiality. That is to say, the important content basically will not be from the “static area” out of half a signal, fundamentally blocked the worries.
This “two-way shielding” role, making the communication shield has become the key confidential communication field of choice. Whether it is a government agency's classified meeting, or business company's trade secrets, or even personal privacy, as long as the absolute security of the “quiet zone”, everything will be easy.
Moreover, the latest generation of communication drone jammers can also be based on demand, the specific 2G/3G/4G/5G/WIFI and other frequency bands to implement precise selective shielding. This allows the user to take into account both communication protection and ease of use, really make the best use of things, twice the result with half the effort.
In the current complex environment with many hidden dangers, communication network blocker is undoubtedly an indispensable “last line of defense” for important confidential communications. With it, no matter what kind of radio wave torture, any eavesdropping interference soul will have no place to hide. It can be said that this small and exquisite “secrecy magic weapon”, will draw a quiet and safe for the important affairs of the absolute territory.
-
 @ 16d11430:61640947
2025-01-22 02:18:40
@ 16d11430:61640947
2025-01-22 02:18:40Payment systems are the backbone of global commerce, enabling trillions of dollars in transactions annually. Traditional fiat-based payment processors, like Visa, Mastercard, and PayPal, dominate the landscape with widespread adoption and established infrastructures. However, Bitcoin and the Lightning Network have emerged as robust alternatives, offering unique advantages in resilience, efficiency, and decentralization. This article explores why Bitcoin Lightning infrastructure is more resilient than traditional payment systems, providing a nuanced comparison of their strengths and limitations.
- Decentralization vs. Centralization
Traditional Payment Systems Traditional systems are centralized, meaning they rely on intermediaries like banks, payment processors, and settlement networks. While centralization enables ease of management and compliance, it introduces critical single points of failure. Outages, regulatory interference, or cyberattacks targeting these centralized entities can disrupt the entire network.
Bitcoin Lightning Network Bitcoin, by design, is a decentralized network where no single entity has control. The Lightning Network, built on top of Bitcoin, inherits this resilience. By distributing transaction processing across a peer-to-peer network, the Lightning Network minimizes risks of downtime or targeted attacks. Nodes operate independently, creating a system that is fault-tolerant and robust under various adverse conditions.
- Resilience to Outages
Traditional Payment Systems Centralized payment processors are vulnerable to outages caused by technical glitches, infrastructure failures, or cyberattacks. For example, payment processing services like Visa have experienced hours-long outages, causing significant disruptions for businesses and consumers. These outages highlight the fragility of relying on centralized servers.
Bitcoin Lightning Network The Lightning Network operates on a globally distributed network of nodes. If one node goes offline, the network continues to function seamlessly. This redundancy ensures that the system remains operational even in the face of localized failures or attacks. Moreover, since the Lightning Network operates over Bitcoin, the underlying blockchain serves as a fallback mechanism for final settlement.
- Transparency and Trust
Traditional Payment Systems Fiat payment systems are opaque, requiring users to trust intermediaries. Chargebacks, fraud, and disputes are resolved through centralized authorities, often leading to delays and inconsistent outcomes. Trust is placed in banks and financial institutions to safeguard funds and execute transactions.
Bitcoin Lightning Network Bitcoin’s public ledger ensures complete transparency, with every transaction recorded immutably on the blockchain. The Lightning Network leverages cryptographic proofs for secure and trustless transactions. Users retain full control over their funds, and the system eliminates the need for intermediaries, reducing risks of fraud and chargeback abuse.
- Cost and Efficiency
Traditional Payment Systems Intermediaries in fiat payment systems charge fees for processing transactions, often passing these costs to consumers and merchants. Cross-border payments are particularly expensive due to currency conversion fees and delays in settlement times. These inefficiencies make fiat systems costly and slow for international commerce.
Bitcoin Lightning Network The Lightning Network significantly reduces transaction costs by enabling near-instant payments without intermediaries. Microtransactions, which are often impractical in traditional systems, become feasible on the Lightning Network due to its low fees. Additionally, cross-border payments are seamless, eliminating currency conversion delays and fees.
- Security and Fraud Prevention
Traditional Payment Systems Centralized payment systems are frequent targets for cyberattacks, including data breaches and fraud. Stolen credit card information can lead to significant financial and reputational damages. The reliance on personal identification information (PII) further exposes users to identity theft.
Bitcoin Lightning Network The Lightning Network utilizes cryptographic protocols to secure transactions. Private keys and digital signatures ensure that only the rightful owner can authorize a transaction. Since the network operates on pseudonymous identities, the risk of identity theft is minimized. Additionally, by removing intermediaries, the Lightning Network reduces the attack surface for cybercriminals.
- Accessibility and Financial Inclusion
Traditional Payment Systems Fiat payment systems require users to have access to bank accounts and credit facilities. This dependency excludes millions of people in developing regions who lack access to formal banking infrastructure. Moreover, stringent KYC (Know Your Customer) and AML (Anti-Money Laundering) requirements create barriers for the unbanked population.
Bitcoin Lightning Network Bitcoin is inherently inclusive, requiring only an internet connection and a wallet to participate. The Lightning Network enhances this inclusivity by enabling faster and cheaper transactions, making it accessible to individuals in underserved regions. By removing the need for traditional banking intermediaries, Bitcoin promotes financial sovereignty for the unbanked.
- Global Reach and Interoperability
Traditional Payment Systems Cross-border interoperability in fiat systems is limited by regulatory barriers, currency differences, and the need for correspondent banking relationships. International transactions often involve multiple intermediaries, resulting in delays and inefficiencies.
Bitcoin Lightning Network The Lightning Network operates on a global scale, unrestricted by borders or currencies. Its interoperability allows users to transact with anyone, anywhere, without requiring additional infrastructure. This global accessibility positions Bitcoin as a truly universal payment system.
- Resilience Against Censorship
Traditional Payment Systems Centralized payment systems are susceptible to censorship by governments, financial institutions, or corporations. Accounts can be frozen, and transactions blocked, often without transparency or recourse.
Bitcoin Lightning Network Bitcoin’s decentralized nature makes it highly resistant to censorship. The Lightning Network inherits this property, ensuring that no central authority can unilaterally block transactions. This resilience is particularly valuable in regions facing economic instability or authoritarian regimes.
Conclusion
While traditional payment systems have provided the foundation for global commerce, their centralized nature introduces vulnerabilities that Bitcoin and the Lightning Network address effectively. By leveraging decentralization, transparency, and cryptographic security, Bitcoin Lightning offers a more resilient and efficient alternative for the digital age. It empowers individuals with financial sovereignty, reduces costs, and fosters inclusivity, making it a compelling choice for the future of payments.
However, the Lightning Network is not without challenges. Adoption remains limited compared to fiat systems, and the user experience can be complex for non-technical users. Overcoming these hurdles will be essential for Bitcoin to achieve mainstream acceptance.
In the end, the resilience of Bitcoin and the Lightning Network lies in their ability to operate without reliance on centralized entities, ensuring that financial systems remain robust, accessible, and censorship-resistant in a rapidly evolving world.
-
 @ 47259076:570c98c4
2025-01-22 02:00:40
@ 47259076:570c98c4
2025-01-22 02:00:40Did I choose the family I was born? Or was it random?
Where do I come from?
Why am I here?
Where am I going?
Perhaps more important than trying to answer those questions, is to know if they are answerable at all, because if it's impossible to know the answer, then attempting to would be a waste of time.
What is wasting time anyways? Perhaps the intention to do something, even if that something is impossible, is a good thing.
Perhaps the value is not in receiving expansive gifts, but in someone making the effort to reward you with anything, even if it's just a piece of paper with a nice message written by hand.
No existential crisis is required, it's all genuine questions.
Is the search for truth infinite?
What is love?
Are people born brave? Or they become brave?
Where my desire to understand myself and the universe comes from?
Are stars watching us? What stars think of us?
Why born in this planet?
Why some people have pleasure in doing evil acts?
At what point should I attempt to control things or just let it go?
One may plan too far in the future and die tomorrow
One may never plan for the future and live until 110 years old, being a homeless
What is energy? Where does it come from?
Can we convert thought into energy?
We have day and night, why not have a third element? Something non binary, something different
Perhaps we already have the third element but our limited perception doesn't allow us to see
Can we increase our perception?
Why good music is harmonic?
Why non human entities are so interested in humanity?
What is the root of all problems?
What is a problem?
What is the price to pay to reach our full potential?
Why?
-
 @ 3efdaebb:3e0d2681
2025-01-22 01:08:58
@ 3efdaebb:3e0d2681
2025-01-22 01:08:58Hey Nostr! It’s App Store release day for Damus. Thanks again to our loyal Purple subscribers for helping us continue to improve the UX and pointing out important changes and fixes. Highlights of Version 1.12:
Added
- Render Gif and video files while composing posts (Swift Coder)
- Add profile info text in stretchable banner with follow button (Swift Coder)
- Paste Gif image similar to jpeg and png files (Swift Coder)
Changed
- Improved UX around the label for searching words (Daniel D’Aquino)
- Improved accessibility support on some elements (Daniel D’Aquino)
Fixed
- Fixed issue where the "next" button would appear hidden and hard to click on the create account view (Daniel D’Aquino)
- Fix non scrollable wallet screen (Swift Coder)
- Fixed suggested users category titles to be localizable (Terry Yiu)
- Fixed GradientFollowButton to have consistent width and autoscale text limited to 1 line (Terry Yiu)
- Fixed right-to-left localization issues (Terry Yiu)
- Fixed AddMuteItemView to trim leading and trailing whitespaces from mute text and disallow adding text with only whitespaces (Terry Yiu)
- Fixed SideMenuView text to autoscale and limit to 1 line (Terry Yiu)
- Fixed an issue where a profile would need to be input twice in the search to be found (Daniel D’Aquino)
- Fixed non-breaking spaces in localized strings (Terry Yiu)
- Fixed localization issue on Add mute item button (Terry Yiu)
- Replace non-breaking spaces with regular spaces as Apple's NSLocalizedString macro does not seem to work with it (Terry Yiu)
- Fixed localization issues in RelayConfigView (Terry Yiu)
- Fix duplicate uploads (Swift Coder)
- Remove duplicate pubkey from Follow Suggestion list (Swift Coder)
- Fix Page control indicator (Swift Coder)
- Fix damus sharing issues (Swift Coder)
- Fixed issue where banner edit button is unclickable (Daniel D’Aquino)
- Handle empty notification pages by displaying suitable text (Swift Coder)
-
 @ 6be5cc06:5259daf0
2025-01-21 23:17:29
@ 6be5cc06:5259daf0
2025-01-21 23:17:29A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ e7968f56:c44b35f3
2025-01-21 22:35:54
@ e7968f56:c44b35f3
2025-01-21 22:35:54The Death of Qualitative Thought
This started off as a message to some friends. I was trying to convince them why it was important that we read Hannah Ardent’s “The Human Condition”. As the message continued to spiral I had to choose another medium to share it with them.
“I'd ask you about love, you'd probably quote me a sonnet. But you've never looked at a woman and been totally vulnerable. Known someone that could level you with her eyes, feeling like God put an angel on earth just for you. Who could rescue you from the depths of hell. And you wouldn't know what it's like to be her angel, to have that love for her, be there forever, through anything, through cancer. And you wouldn't know about sleeping sitting up in the hospital room for two months, holding her hand, because the doctors could see in your eyes, that the terms "visiting hours" don't apply to you. You don't know about real loss, 'cause it only occurs when you've loved something more than you love yourself. And I doubt you've ever dared to love anybody that much.” - Robin Williams in Good Will Hunting
We are on the precipice of a torrent of political and economic change. The global economy is struggling; France can't balance its budget and ousted the prime minister in response, Germany has bungled their energy policy resulting in VW shutting down factories for the first time in its history, contributing to the Chancellor losing a non confidence vote. Both countries have far right parties poised to take leadership, and both these far right parties have advocated for stepping out of the EU. If such an event were to take place it could be the end of the Euro, the second most powerful currency in the world will have been created and destroyed in under 30 years. The UK is in the process of exacerbating their energy woes whilst dealing with a stagnant economy. Likewise, Canada's economy is struggling and the economic minister quit in dramatic fashion due, in part, to terrible budget management. This led to the Canadian prime minister resigning shortly after. China is in a similar economic position and is still trying to stimulate its economy while tensions with the US mount. The US itself is economically resilient and the coming administration’s aggressive approach to economic growth has further bolstered enthusiasm in their economy. This strategy coupled with tariffs will cause inflation to reappear internationally and batter struggling families further. Trump is known to follow an aggressive form of Reganomics that can be understood better as "number go up"; doing whatever it takes to push the economy higher, assuming this will solve society’s woes. Behind Trump stands J.D. Vance and the "Counter Elite", led by Peter Thiel and Elon Musk. Although Musk takes all the attention, it is really Thiel who has the foresight and political cunning to make changes happen. Thiel has been vocal about his opinion on the global economic situation and America’s place in it for quite a while. He has been sounding alarms about economic stagnation, through over regulation, for years. The motto of his venture fund echoes these concerns: "We were promised flying cars, instead we got 140 characters". His main concern being if we constrict growth - increased violence is inevitable. The Department of Government Efficiency (DOGE) will be the "counter elites" first step in reducing government involvement in all facets of society. This new technocracy will display a plethora of metrics to justify their decisions, being STEM oriented individuals. It is important to keep in mind that although these numbers are intended to reflect something from reality, divergences between the metric and what it is intended to measure frequently occur (Campbell’s law). The use of market indices, for example, as a measure of quality of life, is something we frequently see that deviates from most people’s experience. It loses sight of the underlying human issues we are trying to solve. The tech elite frequently display this lack of qualitative understanding; the Cyber Truck or Meta's venture into VR worlds gives a stark display of this. The explanation for the lack of qualitative understanding could be as simple as the inherent societal bias we have between what San Francisco residents would call "Shape Rotators" vs "Wordcels". These terms reflect a general societal view that the humanities carry little to no value, and all decisions should only be made through explicit cause and effect relations. We have been looking at the world through this narrow lens since the 80s, earlier if you ask Hannah Arendt, and the "number go up" approach is only doubling down on this perspective. This world view might be what is the cause of our predicament in the first place. We may have reached a local maximum in terms of moving forward as a society with this strategy, a point of diminishing returns, yet we don't consider others. Our view of the world is only becoming more myopic and our tactics to approach it is becoming more aggressive.
Since Ronald Regan and Milton Freidman pushed "trickle down economics", with their compatriot Margaret Thatcher in the UK, every leader has skewed more to the right. Bill Clinton was far more pro business than democratic presidents prior to him. This trend has only continued. Every President and CEO uses the market as arbiter of success, which employs Friedman's idea that the shareholders are the primary concern (campaign contributors are essentially shareholders) and everything else is secondary. Donald Trump is only refining and pushing these strategies further. He has already signalled tax cuts for the richest people in the country and that he will drop the corporate tax rate to 15%. The market’s exuberance is used to justify these decisions. He has no view of his own of where the country should go, only parroting Regan's campaign slogan, which in itself has no vision of the future.
Trump has been recruited by the tech billionaires since their economic perspectives are aligned. The tech elite have applied the "number go up strategy" to their companies for decades, “hockey stick” growth curves are the only true indicator of success in the industry. Politically they were very liberal, accepting, and sometimes advocating for higher taxes to help state programs. This optimistic hands off approach obviously hasn't worked as San Francisco has become infested with social and political strife, far exceeding issues that comparably sized cities have. Unsurprisingly this has triggered a complete reversal of the tech elites previous views on governance. Now as the tech billionaires enter the political game, they are keen to apply their successful approach in tech to government. Their first application of this strategy will be with the "Department of Government Efficiency", meant to help reduce regulations that are hindering business development.
Silicon Valley has been an ideal case of the benefits of deregulation. The digital world provided a permissionless environment for anyone to build and distribute products. With successes like Google, venture capital funds threw enormous resources behind youthful intelligent founders, and reaped enormous rewards. Building a startup became a common phrase, and achieving the “hockey stick” growth curve became a common dream.Other areas of the world began trying to imitate this model seeing the prosperity it brought to the region. More and more talented youths entered into Computer Science or Computer engineering hoping to join a large software company with generous compensation packages, or founding their own company. Other more regulated industries provided fewer and fewer opportunities as lucrative as tech. This reinforced the perception that tech was the only path to social mobility, and more so, that any field outside STEM is not a valuable investment. The humanities were seen as antithetical to tech, believed to provide zero economic value. This bias is prevalent throughout our society, it is particularly prevalent in San Francisco where the term “wordcel” is used to describe those who prefer to pursue knowledge in the humanities.
What we lost in this was the benefits of qualitative thinking which is more pronounced in the humanities. This is where people learn to analyze things that don’t have clear numerical solutions, to see problems from a multitude of perspectives, to understand that some issues have no clean resolutions, to contemplate what it means to exist and be conscious of your own existence. Humanities are where we learn what the human condition is and how we can improve it. Qualitative thinking allows us to actually consider what we are doing and where we are going. Sean Monahan in his essay “The counter elite won the meme war” captures the lack of qualitative understanding at the core of the tech elite: “the homes of tech billionaires and hundred millionaires I’ve seen (online and otherwise) aren’t much better: generically white and minimal, rectilinear shapes in monochromatic fabrics. You get the sense you are in a third-world luxury hotel that didn’t know you were supposed to hire an interior designer”. Living by the “Number go up” strategy leaves one devoid of taste and depth. It comes painfully obvious, as Sean says of the tech elite: “On a basic level, both their fantasies and realities fail to inspire.” We can plainly see this in the everyday functioning of the companies found in San Francisco over time, as more companies provided high economic output but lower societal value.
This single minded approach to politics and economics has left us bereft of any vigour. San Francisco is overrun with Will Huntings who chose the corporate path. Every aspect of our life has become a cold calculation, even dating has become a numbers game, setting filters and preserving likes. We are left longing for depth and a purpose to pursue that no amount of rigorous number manipulations will provide a substitute for. Leopold Aschenbrenner, part of the super alignment team at OpenAI, mentioned on podcast that he won't spend any money on consumption till he can buy literal galaxies. This comment made me think of Zaphod Beeblebrox, from Hitchhiker’s Guide to the Galaxy, when he awakes on a planet of gold and is overcome with awe, but only a short while earlier he travelled the galaxy on a machine that made the impossible probable and could only think to use it to gain more wealth. What value is a planet of gold when we can’t appreciate the wonders around us?
Even Peter Thiel, the undercover Wordcel who constantly ridicules many fields because they aren't shape rotatory enough, states in his essay "Straussian moment" that the assumption of each individual being a rational economic actor was upended on September 11th. A foundational shift in our society is required to account for this change in our understanding, yet we continue to pursue economics and politics in the same manner, only more aggressively, as if this will produce different results.
What I propose, therefore, is very simple: it is nothing more than to think what we are doing. — Hannah Arendt, The Human Condition.
FIN
-
 @ 000002de:c05780a7
2025-01-21 21:29:39
@ 000002de:c05780a7
2025-01-21 21:29:39The Bellamy salute is a palm-out salute created by James B. Upham as the gesture that was to accompany the Pledge of Allegiance of the United States of America, whose text had been written by Francis Bellamy. It was also known as the "flag salute" during the period when it was used with the Pledge of Allegiance. Bellamy promoted the salute and it came to be associated with his name. Both the Pledge and its salute originated in 1892. It was also known as the "flag salute" during the period when it was used with the Pledge of Allegiance. Bellamy promoted the salute and it came to be associated with his name. Both the Pledge and its salute originated in 1892. Later, during the 1920s and 1930s, Italian fascists and Nazi Germans adopted a salute which was very similar, attributed to the Roman salute, a gesture that was popularly believed to have been used in ancient Rome.[1] This resulted in controversy over the use of the Bellamy salute in the United States. It was officially replaced by the hand-over-heart salute when Congress amended the Flag Code on December 22, 1942.
originally posted at https://stacker.news/items/859191
-
 @ 3c7dc2c5:805642a8
2025-01-21 21:00:47
@ 3c7dc2c5:805642a8
2025-01-21 21:00:47🧠Quote(s) of the week:
'For the love of God, Bitcoin is not a 'scam', and it is not 'going away'. Do yourself some good by honestly and thoroughly researching it, away from mainstream media nonsense. You can thank me and thousands of others on here later.'
'Do you actually understand what it means when the whole world tries to squeeze into a fixed supply digital asset that never gets diluted, is audited every 10 minutes, and trades 24/7 as the most liquid asset on earth? If you do, you’re holding on for dear life.' -Bitcoin For Freedom
🧡Bitcoin news🧡
After a short break from the recap, I am back. I got a new place and I had to focus on that project. Now before I start with this week's Weekly Recap I want to remind all the political larpers (Trump voters etc) of one thing:
THE PROMISE
-
Strategic Bitcoin Reserve
-
Free Ross day one
THE REALITY 1. 47M Wrapped BTC 2. Maybe free Ross later 3. 4.7M tron 4. 47M Ethereum 5. 4.7 M litecoin 6. Pardoned J6 participants
Oh, and he launched the biggest meme/shitcoin, and rug pulled the shit out of it.
On the 12th of January:
➡️Eighth consecutive positive adjustment on the horizon. We saw nine in 2021 and 17 in 2018. This is insane.
➡️A Santander Bank report highlights El Salvador’s booming tourism industry, fueled by Bitcoin adoption. The country announced 3.9M tourists in 2024—a 22% YoY increase and nearly double the levels seen between 2013-2016.
➡️Bitcoin mining difficulty increased by 0.6101% today. The network has programmatically adjusted to a new difficulty level of 110,451,907,374,649 hashes, ensuring the target block time remains stable as global computing power on the network fluctuates.
➡️We now have 7 states, and counting, pushing a Strategic Bitcoin Reserve Bill:
- New Hampshire
- Alabama
- Florida
- Pennsylvania
- Texas
- Ohio
- North Dakota
On the 13th of January:
➡️Italy's largest bank Intesa Sanpaolo has started buying Bitcoin, according to leaked internal emails which celebrate the "first transaction" of €1m for 11 Bitcoin.
➡️The number of Bitcoin addresses holding over 100 BTC has surged by 8.6% since Trump’s election in November.
➡️Ming Shing Group from Hong Kong just acquired 500 Bitcoin for $47M.
➡️Semler Scientific has acquired 237 BTC for ~$23.3 million at ~$98,267 per Bitcoin and has generated a BTC Yield of 99.3% since adopting our BTC treasury strategy in May 2024. As of 1/10/2025, we held 2,321 Bitcoin acquired for ~$191.9 million at ~$82,687 per Bitcoin.
➡️$11.5 trillion BlackRock says that Bitcoin adoption is outpacing the internet and mobile phones.
On the 14th of January:
➡️The Bitcoin network has 610,929x more hashing computational power than the combined total of the world’s top 500 supercomputers.
On the 16th of January:
➡️'Someone just moved 11,000 Bitcoin worth $1.1 BILLION around the world for ONLY $1.50 The world's most efficient monetary network.' - Pete Rizzo
➡️XRP is down 80% from its bitcoin all-time high in 2017. Just don't do shitcoins, it's that simple.
On the 17th of January:
➡️'They did it again! Bindseil and Schaaf published the article, 'Arguments Against a Strategic Bitcoin Reserve'.
It is a wild ride, reaching peak FUD. Maybe even so wild that they had to publish it in a newspaper and not as an ECB blog post. This is ultra bullish' - Dr. Jan Wüstenfeld
➡️Metaplanet's market cap closes above $1 billion for the first time since adopting a Bitcoin Standard.
➡️Jeroen Blokland: ‘Nearly one-fifth of all U.S. states are formally weighing whether to have public funds invest in Bitcoin.’ I am afraid and convinced at the same time that soon, the EU will be the only region still aiming to introduce a central bank digital currency. As a result, it will trigger more polarization, and Europe will lose the Bitcoin battle, just as it hopelessly lost the technology and AI battle.
➡️'ETH was supposed to become deflationary after the "merge" But now the supply is almost back to where it was BEFORE the merge If you're still falling for this shit, you deserve to get scammed.' -Rajat Soni
To make it even worse: 'The ETHBTC ratio is now lower than the day when Coinbase listed it in 2016. You would have been buying ETH at ~$13, but funny enough if you would have just bought and held Bitcoin, you would have actually outperformed it.' -Pledditor.
➡️ First union in Idaho bought Bitcoin.
➡️ California state officials embraced Bitcoin.
➡️Wyoming filed for Strategic Bitcoin Reserve bill.
➡️Massachusetts filed for Strategic Bitcoin Reserve bill. Up to 10% of the $9 Billion Commonwealth Stabilization Fund can be invested in Bitcoin
On the 18th of January:
➡️ Swiss Bitcoin advocates are pushing for the Swiss National Bank to add Bitcoin to the national reserves - Bloomberg They need 100,000 signatures to put it to a national vote.
➡️3.47M Bitcoin addresses hold more than 0.1 BTC. If you own one of them you’re set for life.
➡️Donald Trump dropped a meme coin instead of stacking Bitcoin for a Strategic Reserve. If the president of the UNITED STATES OF AMERICA can launch and promote a memecoin, then essentially it's OK (and not shamed) for anyone/anywhere to do so.
The grift to come is going to be unreal, even by CrApTo standards. A memecoin/shitcoin is a zero-sum* lottery.
There is no wealth creation. Every buy order is simply matched by a sell order. After an initial spike, the price eventually crashes and the last buyers lose everything.
That's the only thing I am going to share on the subject.
➡️Arizona Strategic Bitcoin Reserve bill introduced
The State can invest up to 10% from:
1) State general fund - $28B 2) State retirement funds - $50B
➡️ Bitwise bought +$200 MILLION Bitcoin for its ETF today. The biggest single-day inflow since launching last year.
On the 19th of January:
➡️ Bitcoin Network System Explained in a Chart:
On the 20th of January:
➡️Bitcoin mining difficulty hits a NEW ALL-TIME HIGH.
➡️YouTube rival Rumble started buying Bitcoin for its balance sheet on Friday - CEO
➡️Bitcoin went up 20x in Trump's first term as President. 10x this time?
💸Traditional Finance / Macro:
👉🏽no news
🏦Banks:
👉🏽Global central banks now hold more Gold than at any point in the past 45 years. Something is brewing.
🌎Macro/Geopolitics:
On the 12th of January:
👉🏽Treasuries are entering their 6th year of the third great bond bear market of the last 240 years!
On the 16th of January:
👉🏽EU Commission allows Thierry Breton to take up a new job at Bank of America despite a rule that requires a two-year waiting period before starting lobbying jobs. There are no rules for these corrupt EU (you fill in the blank). The rules apply only to citizens, not to the Brussels elite, and certainly not if you belong to the French political elite.
In December I shared some news on the EU crusade against X. Let me explain this to you in simple terms.
Breton, a man preaching about the ‘rule of law’ and X, while breaching the rules he signed up to himself: ‘Code of Conduct EU Commissioners’. Now read that again. Bitcoin only. Defund politicians.
👉🏽'The Congressional Budget Office just lowered the US population forecast by 11 million, to 372 million in 2054. This implies 6.3% growth over the next 30 years instead of the 10.5% previously expected.
The agency also expects deaths to exceed births starting in 2033, 7 years earlier than in the 2024 estimates. Lower fertility rates and lower net immigration expectations were behind the outlook changes.
Are we heading into a demographic crisis?' - TKL
On the 17th of January:
👉🏽 Germany had 17 nuclear power plants. It shut them all down. Germany spent $1 Trillion for its energy revamp with the following results:
- It is now totally dependent on Russian gas, French nuclear power electricity, and coal (the most polluting fossil fuel)
- Its citizens pay the highest electricity price in Europe
- It causes several times more CO2 per kWh than France Go woke, go broke. $1T for ruining both its economy and environment. Wunderbar!
Just some data: In 2025, Europe is buying Russian gas at an unprecedented pace and spending billions of dollars on it, reports Politico. In the first 15 days of the year, the EU countries imported 837.3 thousand tons of Russian liquified natural gas (LNG).
Just to show you how fucked up things are in the EU. EU companies are backstabbed by their own policymakers.
'Europe's carmakers risk hefty bill for carbon credit from Chinese rivals.'
source: https://www.ft.com/content/677190d1-7d34-4506-a037-418baab67237
I read the article. It’mind-blowingng. It's like shooting a two-barrelled shotgun in your own nuts.
On this point, EU regulators are destroying an entire part of the economy (Car manufacturing + subcontractors) and are giving the keys to Chinese companies. Go woke, go broke. China is making new coal plants at a rate that cancels German / EU efforts 10X or maybe 100x over.
Now from an economic perspective: 'European equities are more or less where they were at the beginning of the century. Overregulation and bureaucracy throttling innovation, and belief in left redistribution nonsense instead of hard work and entrepreneurship have their price.' -Michael A. Arouet
👉🏽Treasuries have experienced their worst rolling 10-year return in 90 YEARS, now at -0.5%. People out here still stacking U.S. gov bonds instead of Bitcoin. Data: U.S. Treasury bonds: -42% - Bitcoin: +809% 'The “smart money” is buying 30-year treasury bonds with a nominal yield of 1.20% on the whim that another investor (or central bank) will buy it from them at a higher price.' -Dylan Leclair
On the 18th of January:
👉🏽Argentina has officially reached its first budget surplus in 14 years. Vamos!
Under Milei’s leadership, Argentina turned a $7.94B trade deficit in 2023 into a record-smashing $18-19B surplus in 2024, surpassing the previous high of $16.89B in 2009. His push to boost energy exports from the Vaca Muerta shale reserves and ramp up grain sales is paying off, making Argentina a global exporting powerhouse again. With inflation already down from nearly 300% to 117.8%, Milei’s economic reforms are proving their worth.
Argentinian President Javier Milei announces "Zero deficit is a reality...promises are fulfilled."
Let me refrain from the above:
➡️Less state
➡️Less government expenses
➡️Capitalism
➡️Free market
👉🏽Wealth exodus accelerated by 157% in 2024: One millionaire leaves Britain every 45 minutes under Labour — Telegraph
157% increase in the outflow of millionaires since Labour came to power - including losing over 10,000 millionaires & 12 billionaires. All these people created wealth in the U.K. through living and spending.
On the 19th of January:
👉🏽U.S. Housing Market 16.2% of Home Purchase Deals were canceled last month, the highest cancellation rate in history
If for some reason people still believe Bitcoin is a Ponzi scheme, well that's their fault. Let me share with you the real Ponzi scheme.
The following chart summarizes the impact of demographics on European pension systems really well:
A ticking time bomb!
The regulatory burdens suffered by citizens are imposed by unelectable bureaucrats! Study Bitcoin.
🎁If you have made it this far I would like to give you a little gift:
Some fountain of Lyn Alden's wisdom:
https://www.youtube.com/watch?v=fZlcrLZkNA8
Lyn Alden is a macro analyst, investment strategist, and the author of Broken Money. In this episode of What Bitcoin Did, they discuss the impact of fiscal policy on inflation, the Federal Reserve's constraints under fiscal dominance, and the role of tariffs in shaping the economic landscape. They also get into a Strategic Bitcoin Reserve, and what Donald Trump’s Administration will mean for Bitcoin.
Credit: I have used multiple sources!
The complete Weekly Recap will be accessible on my Bitcoin Friday page on Habla. Enriched with detailed charts, illustrative images, and comprehensive macroeconomic news to provide context and clarity.
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly. Use the code BITCOINFRIDAY
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple.⠀⠀⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you? If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-
-
 @ f3b691eb:aa9a5c31
2025-01-21 20:53:59
@ f3b691eb:aa9a5c31
2025-01-21 20:53:59I know there are a ton of people working on onboarding resources for new users. Informational sites, user guides, wallet info etc.
Where do you send new users?originally posted at https://stacker.news/items/859149
-
 @ 16d11430:61640947
2025-01-21 20:40:22
@ 16d11430:61640947
2025-01-21 20:40:22In a world drowning in Monopoly money, where people celebrate government-mandated inflation as "economic growth," it takes a special kind of clarity—nay, cynicism—to rise above the fiat circus. This is your guide to shedding your fiat f**ks and embracing the serene chaos of sound money, all while laughing at the absurdity of a world gone fiat-mad.
- Don’t Feed the Clowns
You know the clowns I’m talking about: central bankers in their tailored suits and smug smirks, wielding "tools" like interest rates and quantitative easing. Their tools are as real as a magician's wand, conjuring trillions of dollars out of thin air to keep their Ponzi economy afloat.
Rule #1: Don’t engage. If a clown offers you a hot take about the "strength of the dollar," smile, nod, and silently wonder how many cups of coffee their paycheck buys this month. Spoiler: fewer than last month.
- Turn Off the Fiat News
Do you really need another breathless headline about the next trillion-dollar deficit? Or the latest clickbait on why you should care about the stock market's emotional rollercoaster? Mainstream media exists to distract you, to keep you tethered to their illusion of importance.
Turn it off. Replace it with something sound, like the Bitcoin whitepaper. Or Nietzsche. At least Nietzsche knew we were doomed.
- Mock Their Inflationary Gospel
Fiat apologists will tell you that inflation is "necessary" and that 2% a year is a "healthy target." Sure, because a little robbery every year keeps society functioning, right? Ask them this: "If 2% is healthy, why not 20%? Why not 200%? Why not Venezuela?"
Fiat logic is like a bad acid trip: entertaining at first, but it quickly spirals into existential horror.
- Celebrate the Fiat Freakshow
Sometimes, the best way to resist the fiat clown show is to revel in its absurdity. Watch politicians print money like teenagers running up a credit card bill at Hot Topic, then watch the economists applaud it as "stimulus." It’s performance art, really. Andy Warhol could never.
- Build in the Chaos
While the fiat world burns, Bitcoiners build. This is the ultimate "not giving a fiat f**k" move: creating a parallel economy, one satoshi at a time. Run your Lightning node, stack sats, and laugh as the fiat circus consumes itself in a flaming pile of its own debt.
Let them argue about who gets to rearrange the deck chairs on the Titanic. You’re busy designing lifeboats.
- Adopt a Fiat-Free Lifestyle
Fiat-free living means minimizing your entanglement with their clown currency. Buy meat, not ETFs. Trade skills, not IOUs. Tip your barber in Bitcoin and ask if your landlord accepts Lightning. If they say no, chuckle and say, “You’ll learn soon enough.”
Every satoshi spent in the real economy is a slap in the face to the fiat overlords.
- Find the Humor in Collapse
Here’s the thing: the fiat system is unsustainable. You know it, I know it, even the clowns know it. The whole charade is destined to collapse under its own weight. When it does, find solace in the absurdity of it all.
Imagine the central bankers explaining hyperinflation to the public: "Turns out we can't print infinity after all." Pure comedy gold.
- Stay Ruthlessly Optimistic
Despite the doom and gloom, there’s hope. Bitcoin is hope. It’s the lifeboat for humanity, the cheat code to escape the fiat matrix. Cynicism doesn’t mean nihilism; it means seeing the rot for what it is and choosing to build something better.
So, don’t just reject the fiat clown show—replace it. Create a world where money is sound, transactions are sovereign, and wealth is measured in energy, not debt.
Final Thought: Burn the Tent Down
Aldous Huxley once envisioned a dystopia where people are so distracted by their own hedonistic consumption that they don’t realize they’re enslaved. Sound familiar? The fiat clown show is Brave New World on steroids, a spectacle designed to keep you pacified while your wealth evaporates.
But here’s the punchline: they can only enslave you if you care. By rejecting their system, you strip them of their power. So let them juggle their debts, inflate their bubbles, and print their trillions. You’ve got Bitcoin, and Bitcoin doesn’t give a fiat f**k.
Welcome to the satirical resistance. Now go stack some sats.
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ cff1720e:15c7e2b2
2025-01-21 19:28:49
@ cff1720e:15c7e2b2
2025-01-21 19:28:49Introduction
The aim of ELI5 (explain me like I'm 5) is to explain difficult things simply. This is urgently needed in our high-tech world, because only by understanding the technologies can we use them properly and develop them further.
I'm starting my series with Nostr, a relatively new internet protocol. What the hell is an Internet protocol? In formal terms, it is an international standard that has ensured that the Internet has been working pretty well for over 30 years. It is the language in which computers communicate with each other and which you also use every day, probably without realizing it. http(s) transports your request to a server (e.g. Amazon), and html ensures that a nice page is created on your screen from the data supplied. A mail is sent to the mail server with smtp and retrieved from it with imap, and since everyone uses the standard, this works with every app on every operating system and with every mail provider.
And with an e-mail address like roland@pareto.space, you can even move at any time, no matter where. Cool, that's state of the art! But why doesn't this work with chat, for example, is there no protocol? Yes, it's called IRC (Internet Relay Chat → remember the name), but it's hardly ever used. The reasons for this are not technical, but rather apps such as Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok and others have deliberately created incompatibilities and user dependencies in order to maximize profits.

Since the standard protocol is not used, each app has its own, and we need a handful of apps to exchange information with everyone we know. A mobile phone number is a prerequisite for every account, allowing app manufacturers to track users comprehensively and earn up to USD 30 per account per month by selling the information. The user is no longer the customer, he is the product! Advertising SPAM is the least of the problems with this business model. Servers with millions of user data are a “honey pot”, so they are often hacked and the access data sold. In 2024, the Twitter account of then President Joe Biden was also hacked and no one knew who had written the messages (nor did they before), meaning that the authenticity of the content is not guaranteed with any of these providers. In the same year, the founder of Telegram was taken into custody in France because he refused to build backdoors into his software. Now, to protect “our democracy”, practically anyone can read what information they exchange with whom, e.g. which shampoo certain politicians use.

Why Nostr?
And anyone who actually believes they can practice freedom of expression on social media will quickly find themselves in the situation of Donald Trump (who was president at the time), whose Twitter account was shut down in 2021 (cancel culture). The user data, i.e. their profile, contacts, documents, images, videos and audio files - no longer belong to them anyway but are the property of the platform operator; read the terms and conditions. But no, not a good idea, there are hundreds of pages and they are constantly being changed. So everyone uses apps whose technology they don't understand, whose rules they don't know, where they have no rights and which steal the results of their actions. What would the five-year-old say if his older sister offered to “manage” all his toys and then hand them over if he was good? “You must be crazy”, and with that the toddler proves he has more sense than the majority of adults.
Conclusion: no standards, no data, no rights = no future!

How does Nostr work?
The developers of Nostr realized that the server-client concept had turned into a master-slave concept. The master is synonymous with centralization and becomes the “single point of failure”, which inevitably makes systems dysfunctional. In a distributed peer2peer system, there are no longer any masters but only equal nodes (relays) on which the information is stored. By storing information redundantly on several relays, the system is more resilient in every respect. It is not only nature that has successfully used this principle for millions of years, the Internet was also designed in this way (the ARPAnet was developed by the US military for use in war situations with massive disruptions). All nostr data is stored on relays and the user can choose between public (usually free) and private relays, e.g. for closed groups or for the purpose of data archiving. As documents are stored on several relays, unique document names (URIs = identifiers) are used instead of URLs (locators), making broken links a thing of the past, as are deletions / losses.
Each document (called an event) is signed by the owner, making it authentic and tamper-proof and can only be deleted by the creator. A key pair consisting of a private (nsec) and public key (npub) is used for this, as known from mail encryption (PGP). This represents a Nostr identity that can be supplemented with a picture, name, bio and a readable Nostr address (e.g. roland@pareto.space ), which is all that is needed to use all the resources of the Nostr ecosystem. And this now consists of over a hundred apps with different focuses, e.g. for personal encrypted messages (DM → OxChat), short messages (Damus, Primal), blog posts (Pareto), meetups (Joinstr), groups (Groups), images (Olas), videos (Amethyst), audio chat (Nostr Nests), audio streams (Tunestr), video streams (Zap.Stream), marketplaces (Shopstr) and much more. Registration is done with a single click (single sign-on) and ALL user data is available to the apps (profile, data, contacts, social graph → followers, bookmarks, comments, etc.), in contrast to the fragmented data silos of the present.
Summary: one open standard, all data, all rights = great future!

Why is Nostr the future of the internet?
“Don't build your house on someone else's property” also applies to the Internet - for all app developers, artists, journalists and users, because their data is also valuable. Nostr guarantees ownership of the data and overcomes its fragmentation. Neither use nor creative freedom is restricted by excessive license and usage conditions. Passive users become active participants through interaction, co-creators in a sharing economy (Value4Value). Open source finally restores trust in software and its providers. Open standards enable developers to cooperate more and develop faster, while guaranteeing freedom of choice for users. Which brings us back to our five-year-old for the last time. Children love Lego more than anything, especially the maxi box “Classic”, because it allows them to live out their imagination to the full in terms of combinations. Adults then give them the far too expensive theme packs, with which you can only build one solution according to the instructions. “What's wrong with my parents, when did they take a wrong turn?” the children rightly ask themselves. But the image can be polished up again if they show their children Nostr, because even five-year-olds understand the advantages.
The new Internet is decentralized. The new Internet is self-determined. Nostr is the new Internet.

\ More infos: https://nostr.net/\ Quick start: https://start.njump.me/
-
 @ 62a6a41e:b12acb43
2025-01-21 19:19:06
@ 62a6a41e:b12acb43
2025-01-21 19:19:06Bodhidharma, the founder of Zen Buddhism (also known as Zen or Zen meditation), meditated for nine years, simply looking at a wall.
Nine years staring at a wall.
Good things take time. Don’t be afraid to take your time. Forget what Western society has taught us—here, we are slaves to time and productivity.
I believe one of the reasons the Western world is in decline is precisely because we lack the philosophical and religious structures that enable true freedom and focus on understanding.
Christianity is beautiful in its own way, but it simply isn’t as clear or rational as Eastern philosophy. As a result, it hasn’t managed to foster an environment for genuine seekers or free thinkers in the same way.
We need to take the time to think. The West doesn’t understand that.
Take your time. You are free to take your time. It's your time. Take as much time as you want, until you understand what you needed to understand.
-
 @ 47f5dcf7:b16eadfa
2025-01-21 18:56:07
@ 47f5dcf7:b16eadfa
2025-01-21 18:56:07The loss of sight is a grim tragedy. Are there words capable of describing the sorrow of once having been able to witness this world and all that it contains, bathed in it's wonderful colours, complimented by the symphony that the contrasts between them orchestrate; of having seen expressions on people's faces that sometimes amplify and sometimes betray the emotions of their person; of having had the agency of finding meaning in the beauty and forms of objects around you by virtue of the concepts you had read? If there are any words whose meaning can bear the burden, I am incapable of stringing them together.
Tennyson believed that "'Tis better to have loved and lost, than never to have loved at all". I reframe this line to ask you not about the experience of love, but the experience of sight; "Is it better to have sight and lost it, than to never have seen at all?" Whatever choice one prefers, the conclusion is still tragic. I ask this question not for the sake of literary flair, but because I do believe this is the predicament most of us find ourselves in without even being minutely aware of it.
Allah, in His infinite wisdom, has endowed His creation with senses on par with their purpose. The sunflower has no eyes, yet it tracks the sun, seeking the sunlight that will fuel it's photosynthesis, fulfilling it's purpose of growth. The animals possess eyes that are fine-tuned for their purpose of survival with predators having better depth perception and prey having a better field of vision. Humans also have eyes, but humans are not animals. While sharing the same basic requirements of the body, we have an intrinsic realisation that we were made for something more. If we were made for more, shouldn't our ability to see be greater than an animal's?
Allah has made our eyes capable of seeing realities deeper than the soul and greater than the expanse of the universe. Our eyes do not just serve to capture the sun-rays reflected from a towering snow-capped peak to create the image of a mountain in our brains. Rather, the eyes of the body and the eyes of the soul are meant to work in conjunction to generate an overwhelming sense of awe in our hearts that compels us to reflect on the magnificence of the One Who is capable of creating multitudes of these colossal mountains. That is true "sight". Bani Adam's purpose is to recognise, know, and submit to Allah willingly and we have been given eyes that serve that purpose. If our eyes cannot yet acknowledge Him in the objects and events around us, then our example is of those
"...hearts they do not understand with, eyes they do not see with, and ears they do not hear with. They are like cattle. In fact, they are even less guided! Such ˹people˺ are ˹entirely˺ heedless." (7:179)
In conclusion, all I can do is ask myself, "Can I see? Was I ever able to see? Or is it that I have lost the ability to see?" Allahu A'lam
-
 @ 0f061fe4:944cdb2b
2025-01-21 18:46:56
@ 0f061fe4:944cdb2b
2025-01-21 18:46:56There are too many ways to build and test a project with CMake. On the other hand, there is too little knowledge out there about those ways. As a consequence, people wrap the CMake invocation in custom scripts written in Bash, Python, Typescript etc.
Just look at the Jenkins configuration in your company. Look at different implementations of GitHub actions/workflows for CMake. I bet what you will find is a complete framework with custom abstractions of core utilities, version control systems, the CMake command line, the actual build system, and more.
Looking at the commands that actually perform the steps for configuring, building, and testing, it is very likely that you see those:
sh mkdir -p $build_dir cd $build_dir cmake -G Ninja $source_dir ninja ninja testI assume you know that CMake can create the build directory and provides an abstraction for invoking the actual build system. You should also know that the
testtarget essentially just runsctest. So you could simplify and generalize the above commands to this:sh cmake -G Ninja -S $source_dir -B $build_dir cmake --build $build_dir ctest --test-dir $build_dirBut did you know that CTest already provides a command line abstraction to execute the three steps?
sh ctest --build-and-test $source_dir $build_dir \ --build-generator Ninja --test-command ctestDon't ask me why the above command stops after the build step when
--test-command ctestis omitted. After all, this mode is called "build and test", so just executingctestwould be a sane default when no test command is explicitly set by the user.Anyway, there is more. CTest also provides abstractions for the version control system, coverage analysis, and memory ckecking. But here be dragons. There are, believe it or not, four different ways to configure CTest as a dashboard client:
- CTest Command-Line
- Declarative CTest Script (undocumented)
- CTest Module
- CTest Script
In the first approach, the command-line flag
-Dor a combination of-Mand-Tis used to control which steps to execute. The actual logic that is executed for those steps is controlled through a configuration file calledDartConfiguration.tclwhich is read from the current working directory.Note that the documentation claims that this approach works in an already-generated build tree. This is not true in all cases. What is definitely needed, is that the source repository is already checked out.
While the source directory can be updated, it cannot be initialized with this approach. We will get back to those details later. For now, copy the following content into a file calledDartConfiguration.tcl:tcl SourceDirectory: Example BuildDirectory: Example-build UpdateCommand: git ConfigureCommand: cmake -G Ninja -DCMAKE_C_FLAGS_INIT=--coverage .. CoverageCommand:gcov MemoryCheckCommand: valgrindMake sure that
Exampleis a directory next to theDartConfiguration.tclfile and contains a local clone of a git repository. Then execute the following:sh ctest -M Experimental \ -T Start \ -T Update \ -T Configure \ -T Build \ -T Test \ -T Coverage \ -T MemCheckObserve in the output that ctest updates the repository to the latest revision, configures the project, builds it, runs the tests, analyzes the coverage, and finds some memory leaks.
In the second approach, the
DartConfiguration.tclfile is replaced with a file written in the CMake syntax:cmake set(CTEST_SOURCE_DIRECTORY "/home/dpfeifer/Example") set(CTEST_BINARY_DIRECTORY "/home/dpfeifer/Example-build") set(CTEST_COMMAND "ctest") set(CTEST_CMAKE_COMMAND "cmake") set(CTEST_CVS_CHECKOUT "gh repo clone Example")The name of the file does not really matter. I use the name
CTestScript.cmakeand invoke ctest like this:sh ctest --script CTestScript.cmake --verboseRemember that, with the previous approach, it was impossible to initialize the source directory? With this approach, it is possible via the
CTEST_CVS_CHECKOUTvariable. Despite the name, this variable can be used to checkout a repository with any version control system, as shown in the example. However, updating probably only works with CVS.What is worse, is that this approach basically just handles the
update,configure, andteststeps. Yes, the project is not even built before running the tests. I wonder if anyone finds this useful.Why am I even mentioning this approach when it is so barely useful? Because it can get in the way when you don't expect it. I will get back to that.
The third approach also allows setting variables in the CMake syntax. Not in a separate file, but in the top level project's
CMakeLists.txtfile, right beforeinclude(CTest). This module internally callsconfigure_fileto placeDartConfiguration.tclinto the build tree.Now, it becomes clear why the documentation claims that
ctestmay be invoked with command-line flags-D,-M, and-Tin an already-generated build tree: Because the CTest module placesDartConfiguration.tclthere. It also becomes clear under which circumstance it does not work as advertized: When the project does notinclude(CTest)!But when a project does
include(CTest), it will get several custom targets likeExperimentalCoveragethat will executectest -D ExperimentalCoverage.
The last approach uses the same file and command-line as the second one. The difference is that the build-and-test logic is scripted with CTest commands:
```cmake cmake_minimum_required(VERSION 3.14)
set(CTEST_SOURCE_DIRECTORY "/home/dpfeifer/Example") set(CTEST_BINARY_DIRECTORY "/home/dpfeifer/Example-build") set(CTEST_CMAKE_GENERATOR "Ninja") find_program(CTEST_GIT_COMMAND "git") find_program(CTEST_COVERAGE_COMMAND "gcov") find_program(CTEST_MEMORYCHECK_COMMAND "valgrind")
cmake_host_system_information(RESULT NPROC QUERY NUMBER_OF_LOGICAL_CORES)
if(NOT EXISTS ${CTEST_SOURCE_DIRECTORY}) set(CTEST_CHECKOUT_COMMAND "gh repo clone Example") endif()
ctest_start("Experimental") ctest_update() ctest_configure(OPTIONS -DCMAKE_C_FLAGS_INIT=--coverage) ctest_build(PARALLEL_LEVEL ${NPROC}) ctest_test(PARALLEL_LEVEL ${NPROC}) ctest_coverage() ctest_memcheck(PARALLEL_LEVEL ${NPROC}) ```
This is the only approach that can both initialize and update the source directory. It is also the only approach that allows you to execute the same step more than once. Imagine you want to use a multi-config generator and then run
ctest_buildfor each configuration. It gives full control over the logic what steps to run under what conditions. Imagine you want to run the expensive memory checking only when the build finishes without warnings, as the warnings may already indicate memory issues. The possibilities are endless.
How does
ctest --scriptdistinguish between "CTest Script" mode and the dreaded "Declarative CTest Script" mode?At the beginning of the script, CTest implicitly sets the variable
CTEST_RUN_CURRENT_SCRIPTto 1. Each of thectest_*functions sets the variable to 0. When this variable is still 1 at the end of the script, CTest assumes that none of thectest_*functions have been called. However, when thectest_*functions are called from inside a scoped block, there may be cases when the variable is unchanged. In such cases, it is necessary to explicitlyset(CTEST_RUN_CURRENT_SCRIPT 0).
My recommendation to everyone who wants to setup a CI system for CMake projects is to use a CTest Script. For an example GitHub action built using a CTest script have a look at purpleKarrot/cmake-action.
The fact that there are so many different approaches to the same use case is an issue in my optionion. Also, the user experience of the CTest scripts needs to be improved. I have some ideas how those issues can be addressed. I will write about them in a follow up.
-
 @ 6e15bf3d:0548a961
2025-01-21 18:46:37
@ 6e15bf3d:0548a961
2025-01-21 18:46:37As we approach 2025, website design continues to evolve at a rapid pace, driven by innovations in technology, shifts in user behavior, and an increasing focus on providing personalized experiences. Web design is not just about creating visually appealing layouts anymore; it is now about creating functional, intuitive, and immersive experiences that make users feel connected with the brand. As businesses and content creators recognize the importance of digital presence, staying on top of the latest trends will be crucial for success in the upcoming year.
In this article, we will explore the top website design trends for 2025, including technological advancements, aesthetic shifts, and user experience (UX) enhancements that will shape the future of the web.
**2. 1. AI-Powered Personalization ** Artificial Intelligence (AI) has made a profound impact on website design, enabling businesses to offer highly personalized experiences. AI-powered tools will continue to transform websites by analyzing user behavior and preferences to deliver tailored content, recommendations, and interfaces. These personalized features enhance user engagement, increase conversion rates, and improve overall customer satisfaction.
In 2025, we can expect to see more websites integrating AI technologies that adjust content, layout, and even color schemes based on individual user profiles. Personalized experiences help create a sense of relevance and connection, making users feel as though the website was designed specifically for them.
**3. 2. Immersive Experiences with VR/AR ** Virtual Reality (VR) and Augmented Reality (AR) technologies are no longer just futuristic concepts; they are becoming increasingly accessible and practical in web design. In 2025, expect websites to offer immersive experiences using AR and VR. This could mean users experiencing products in a 3D environment, virtually trying on clothes, or even exploring a property from the comfort of their home.
With the advancement of 5G technology, websites can incorporate these technologies more smoothly, providing a seamless and engaging experience. Retailers, real estate agencies, and travel companies, in particular, will benefit from offering interactive experiences that allow users to interact with their products and services in new and exciting ways.
For example, an e-commerce site might allow you to place a piece of furniture in your room via AR to see how it fits. For the real estate sector, virtual tours of homes or apartments can be offered with VR, helping users feel more confident in their decisions before visiting in person.
**4. 3. Mobile-First Design ** As mobile device usage continues to dominate the internet landscape, mobile-first design is expected to be a leading trend in 2025. In fact, more than 54% of global web traffic now comes from mobile devices (source: Statista), a statistic that reflects the increasing importance of responsive web design that prioritizes mobile experiences.
A mobile-first approach means designing websites primarily for smaller screens, ensuring that the content is easily accessible, readable, and navigable on smartphones and tablets. Designers will focus on optimizing touch interactions, speed, and performance on mobile devices to meet user expectations.
**5. 4. Minimalistic and Clean Aesthetics ** While overly complex and cluttered web designs were once the norm, the trend has been shifting towards minimalism. Clean and simple designs, with plenty of white space, allow for better navigation, faster load times, and a more focused user experience. In 2025, this trend will continue as users demand simplicity and speed when interacting with websites.
Minimalist design involves reducing elements to the essentials, eliminating distractions, and using whitespace strategically to highlight key content. Bold typography, crisp images, and well-organized layouts will allow the content to speak for itself without overwhelming the user. The minimalist approach also tends to work well with responsive design, ensuring that websites are easy to navigate regardless of the device or screen size. Furthermore, this trend aligns with sustainability efforts, as minimalist designs often reduce the need for heavy graphic elements, leading to faster loading times and reduced energy consumption.
**6. 5. Dark Mode and Customizable Themes ** Dark mode has become a popular feature in web design, and it is set to stay in 2025. Offering users the ability to toggle between light and dark modes not only enhances accessibility but also reduces eye strain, especially in low-light conditions. In addition, dark mode can give websites a modern and sleek aesthetic that appeals to users.
Many websites will implement customizable themes, allowing users to choose their preferred visual experience. Whether it’s adjusting colors, fonts, or background styles, offering theme customization can make users feel more in control of their experience, making it more likely that they’ll engage with the content for longer periods.
**7. 6. Microinteractions and Animations ** Microinteractions are small, interactive animations or design elements that help users navigate and engage with a website. These subtle animations provide feedback, guide users through processes, and add a sense of interactivity to the experience. For example, hover effects, button animations, and loading animations are all types of microinteractions.
In 2025, websites will incorporate even more sophisticated microinteractions, making websites feel more dynamic and engaging. These small details enhance the user experience by making interactions feel more intuitive and enjoyable. However, it’s crucial that designers balance animations and microinteractions with site performance, as excessive animations can slow down load times.
**8. 7. Voice Search and Voice User Interface (VUI) ** As voice search technology becomes more advanced, websites will need to adapt to this growing trend. Voice search allows users to interact with a website using spoken commands, and it is especially useful for mobile and smart device users who prefer hands-free experiences.
By 2025, voice search will become more integrated into website design, as businesses will optimize their content for voice queries. Websites will also implement voice user interfaces (VUI) that allow users to navigate and interact with websites through voice commands. This trend is particularly important as voice-activated assistants like Siri, Google Assistant, and Alexa continue to gain popularity.
**9. 8. Typography as a Design Element ** Typography has always been an essential part of web design, but in 2025, it will become even more central to the overall design aesthetic. Bold, experimental typography is taking center stage as designers use fonts to convey personality, emotion, and style.
From oversized text to custom fonts, typography is no longer just a functional element; it is a visual statement that enhances the identity of a brand. In addition to bold typography, variable fonts that allow for greater flexibility in font weight, size, and style will become more popular, enabling websites to create more dynamic and personalized typographic experiences.
**10. 9. Sustainability in Design ** As environmental consciousness grows, sustainability will become a driving factor in website design. In 2025, expect to see more brands and web developers embracing eco-friendly design practices. This includes designing websites that minimize their environmental impact by reducing energy consumption and optimizing site speed.
Sustainable design could involve using lighter graphic elements, optimizing images and videos for faster loading, and choosing energy-efficient hosting options. Reducing the carbon footprint of websites is an essential part of future web design, especially as consumers become more aware of the environmental impact of digital technologies.
**11. 10. Inclusive and Accessible Design
**Web accessibility continues to be a priority for designers, and in 2025, we will see further advancements in this area. Websites will become even more inclusive, with features such as adjustable text sizes, color contrast settings, and screen reader compatibility.
Designers will also implement accessibility guidelines and best practices to ensure that all users, including those with disabilities, can access and navigate websites easily. This includes creating more intuitive navigation systems, providing alternative text for images, and ensuring that content is accessible for people with visual, auditory, or motor impairments.
Web accessibility is not just a legal requirement in some regions but also a moral responsibility. By making websites accessible to everyone, businesses can ensure a more inclusive online experience for all users.
**Conclusion ** As we move towards 2025, website design will continue to innovate, with new technologies and aesthetic shifts leading the way. From AI-powered personalization and immersive AR/VR experiences to minimalistic aesthetics and mobile-first design, the future of web design is focused on user-centric experiences that are visually striking, easy to navigate, and accessible to all. To stay ahead in this ever-evolving landscape, businesses and website developers must embrace these trends and ensure that their websites are both functional and forward-thinking. By doing so, they will not only enhance the user experience but also build stronger connections with their audience, ultimately leading to greater success in the digital world. The future of website design is bright, and 2025 promises to bring about exciting changes that will redefine how we interact with the web.
-
 @ b17fccdf:b7211155
2025-01-21 18:39:47
@ b17fccdf:b7211155
2025-01-21 18:39:47~ > Check out the steps to get this ~ > HERE < ~
Note: for different reasons, it is recommended choosing Option 1: DoT & DNSSEC using systemd-resolved, but you could want to use Option 2, choose behind your criteria, both are valid to achieve the same objective.
Some more changes were released recently in other places of the MiniBolt guide, check the full release notes:
Full release notes
~ > Static IP & custom DNS servers bonus guide:
- Adds custom DNS server suggestions.
- Adds different steps to check the changes after configurations.
- Deleted some unnecessary steps.
- Fix some nits.
~ > Modifications on Configuration (
bitcoin.conf) of Bitcoin Core:- Replace proxy value parameter to use UNIX domain socket (
proxy=unix:/run/tor/socks) | (recently enabled on Bitcoin Core v28). - Replace
startupnotify=chmod g+r /home/bitcoin/.bitcoin/.cookietorpccookieperms=groupBitcoin Core PR. - Adds another special bind address to listen to incoming connections from Tor (
bind=127.0.0.1=onion) | (recently changed on Bitcoin Core v28). - Modified systemd service to improve the startup and shutdown process.
Note: remember to restart Bitcoin Core and reload the systemd with
sudo systemctl daemon-reloadto apply changes.
~ > Delete unnecessary parameters of the systemd service of Lightning client.
Note: remember to reload the systemd with
sudo systemctl daemon-reloadto apply changes.
~ > Others:
- New i2pd webconsole section.
- Adds a new "Validation" subsection to the guides to clarify when checks begin.
- New "Use the Tor proxy from another device" section.
- Adds Electrs compatible with Testnet4 on Testnet bonus guide.
- Adds how to build a Guard/Middle relay section on "Tor services: bridges & relays" bonus guide.
- Adds Extras (optional) section to "Tor services: bridges & relays" bonus guide with different utilities like install Nyx, how to "Limit bandwidth" and others.
- Changed Electrs ports to enable simultaneous mode with Fulcrum.
- Updated aliases list to include news additions in line with updates.
- Updated the Networkmap resource to include news additions in line with updates and migrate to a dynamic visual mode.
- Reorganized some menu items and sections to improve the UX and make more sense in the face of the future.
- Restructure and rename the "Tor obfs4 bridge" bonus guide to "Tor services: bridges & relays" and modify it to run the obfs4bridge, relays, and the master, in separate instances.
- Hidden NYM mixnet and Sparrow server bonus guides from the menus due to disuse or poor performance. Note: it will continue to be maintained later if the situation changes due to the development of the associated software.
- Bump version of various services.
~ > Coming soon...
- Enable DNSSEC for your domain using Cloudflare + Namecheap.
- Enable DoH on:
- Desktop/Android browser (Windows/Linux).
- OS: Windows 11 // Linux (Completed ✅)
- Router.
- Enable DoT on:
- Android OS.
- OS: Windows 11 // Linux (Completed ✅) with DNSSEC verification included.
- Router.
Enjoy it MiniBolter!💙
-
 @ b17fccdf:b7211155
2025-01-21 18:33:28
@ b17fccdf:b7211155
2025-01-21 18:33:28
CHECK OUT at ~ > ramix.minibolt.info < ~
Main changes:
- Adapted to Raspberry Pi 5, with the possibility of using internal storage: a PCIe to M.2 adapter + SSD NVMe:
Connect directly to the board, remove the instability issues with the USB connection, and unlock the ability to enjoy higher transfer speeds**
- Based on Debian 12 (Raspberry Pi OS Bookworm - 64-bit).
- Updated all services that have been tested until now, to the latest version.
- Same as the MiniBolt guide, changed I2P, Fulcrum, and ThunderHub guides, to be part of the core guide.
- All UI & UX improvements in the MiniBolt guide are included.
- Fix some links and wrong command issues.
- Some existing guides have been improved to clarify the following steps.
Important notes:
- The RRSS will be the same as the MiniBolt original project (for now) | More info -> HERE <-
- The common resources like the Roadmap or Networkmap have been merged and will be used together | Check -> HERE <-
- The attempt to upgrade from Bullseye to Bookworm (RaspiBolt to RaMiX migration) has failed due to several difficult-to-resolve dependency conflicts, so unfortunately, there will be no dedicated migration guide and only the possibility to start from scratch ☹️
⚠️ Attention‼️-> This guide is in the WIP (work in progress) state and hasn't been completely tested yet. Many steps may be incorrect. Pay special attention to the "Status: Not tested on RaMiX" tag at the beginning of the guides. Be careful and act behind your responsibility.
For Raspberry Pi lovers!❤️🍓
Enjoy it RaMiXer!! 💜
By ⚡2FakTor⚡ for the plebs with love ❤️🫂
- Adapted to Raspberry Pi 5, with the possibility of using internal storage: a PCIe to M.2 adapter + SSD NVMe:
-
 @ b17fccdf:b7211155
2025-01-21 18:30:13
@ b17fccdf:b7211155
2025-01-21 18:30:13~ > Available at: https://minibolt.info
~> It builds on a personal computer with x86/amd64 architecture processors.
~> It is based on the popular RaspiBolt v3 guide.
Those are some of the most relevant changes:
- Changed OS from Raspberry Pi OS Lite (64-bits) to Ubuntu Server LTS (Long term support) 64-bit PC (AMD64).
- Changed binaries and signatures of the programs to adapt them to x86/amd64 architecture.
- Deleted unnecessary tools and steps, and added others according to this case of use.
- Some useful authentication logs and monitoring commands were added in the security section.
- Added some interesting parameters in the settings of some services to activate and take advantage of new features.
- Changed I2P, Fulcrum, and ThunderHub guides, to be part of the core guide.
- Added exclusive optimization section of services for slow devices.
~ > Complete release notes of the MiniBolt v1: https://github.com/twofaktor/minibolt/releases/tag/1.0.
~ > Feel free to contribute to the source code on GitHub by opening issues, pull requests or discussions.
Created by ⚡2 FakTor⚡
-
 @ b17fccdf:b7211155
2025-01-21 18:22:51
@ b17fccdf:b7211155
2025-01-21 18:22:51😱 Did you recently find this signature verification error when you tried to update your MiniBolt repositories with ->
sudo apt update? 💥🚨👇
🔧 Don't worry, that's because Tor renewed its signing key since it expired last 07/15, just renew your keyring by following the next steps to solve this problem:
~ > CLICK HERE < ~
Enjoy it MiniBolter!💙
-
 @ b17fccdf:b7211155
2025-01-21 18:10:10
@ b17fccdf:b7211155
2025-01-21 18:10:10Link to the bonus guide ~ > HERE <~
Some notes:
ℹ️ For the moment, this guide will touch only the case of an only testnet mode situation, in the future, we will study adding the case of configuration to enable the parallel/simultaneous mode (mainnet+testnet in the same device) in an extra section in this guide.
ℹ️ The services mentioned in this guide are those that have been tested using testnet configuration and these worked fine. Later, in the next versions of this guide, we will go to adding other processes to adapt other services to the testnet mode.
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 18:04:28
@ b17fccdf:b7211155
2025-01-21 18:04:28Available at: https://minibolt.info
Main changes to the version 1:
- The complete guide has been migrated to the new design visual builder web tool platform gitbook.com
- New modern UI (responsive, full width, and better visual items)
- New menu structure for a better user experience
- New visual items to improve the navigation through the web page
- New switch to enable light/dark theme
- Enabled Cloudflare Proxy for maximum protection against attacks and better management of the domain
Other changes:
- New MiniBolt Linktr forked of the alternative FOSS project proposed by Gzuuus
- Changed MiniBolt from a personal project to an organization so that the project has its own identity
- New email contact address hello@minibolt.info to receive proposals and give support
- New resources folder with the current MiniBolt roadmap, network map diagrams, and others
ℹ️ More info:
- The new version is available with the known domain: minibolt.info but from now on links associated with the new v2 version were shared using the v2.minibolt.info subdomain due to a GitBook limitation
- The old and deprecated v1 will be still available at a time in the subdomain v1.minibolt.info, but is in the roadmap delete it definitely in the future, take note ASAP of all that you need of that version before this happens
- Contributors and collaborators will be able to continue doing PR through code programming or using the design block builder gitbook.com
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 17:58:35
@ b17fccdf:b7211155
2025-01-21 17:58:35The router reserves the IP address of the device for a time after going out, but if the device goes out some time, the next time that the device starts, the router could assign a different IP and you could lose access to your node. To avoid this, you need to set a static IP to your MiniBolt.
~ > In addition, you can customize your DNS servers to improve your privacy, normally your ISP, gives you the router with its own DNS servers set by default, and this does that you expose all of your navigation trackings to your ISP, affecting seriously your privacy.
~ > This bonus guide includes all of the necessary steps to get this and is available ~ > HERE < ~

Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 17:47:28
@ b17fccdf:b7211155
2025-01-21 17:47:28Link to the bonus guide ~ > HERE < ~
Some sections of the guide:
- Generate SSH keys
- Import SSH pubkey
- Connect to the MiniBolt node using SSH keys
- Disable password login
- Disable admin password request
Some shortcuts to the Extra sections:
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 17:39:34
@ b17fccdf:b7211155
2025-01-21 17:39:34Link to the bonus guide ~ > HERE < ~
⏰ Recently added an update that includes a new section How to detect Ordinals transactions and verify Ordisrespector filter works to verify that Ordispector is filtering and burning Ordinals correctly 🔥
Fuck Ordinals🤡🔫 and enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 17:29:54
@ b17fccdf:b7211155
2025-01-21 17:29:54Some sections inside of the guide:
- Set up Dynamic DNS
- Wireguard VPN server & client side configurations
- Install & configure the WireGuard VPN Client on a mobile phone
- Configure additional servers & clients
- Use your router’s DDNS preconfigured provider
- Port forwarding on NAT/PAT router
Link to the bonus guide HERE
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 17:19:12
@ b17fccdf:b7211155
2025-01-21 17:19:12Do you want to use a different disk to store data (blockchain and other databases) independently of the disk of the system?
A step-by-step guide using a secondary disk to store the data (blockchain and other databases) independently of the disk of the system and using the Ubuntu Server guided installation.
What's changed
- Rebuilt the Ubuntu Server installation guide based on this bonus guide added.
- Added GIFs to improve the illustration of the steps to follow.
- Case 1: during the Ubuntu server guided installation.
- Case 2: build it after system installation (by command line).
~ > Link to the bonus guide HERE
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 17:07:47
@ b17fccdf:b7211155
2025-01-21 17:07:47 -
 @ b17fccdf:b7211155
2025-01-21 17:02:21
@ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor introduced officially a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks.
~ > This feature at the moment, is deactivate by default, so you need to follow these steps to activate this on a MiniBolt node:
- Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing
tor --versionExample of expected output:
Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0~ > If you have v0.4.8.X, you are OK, if not, type
sudo apt update && sudo apt upgradeand confirm to update.- Basic PoW support can be checked by running this command:
tor --list-modulesExpected output:
relay: yes dirauth: yes dircache: yes pow: **yes**~ > If you have
pow: yes, you are OK- Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added
sudo nano /etc/tor/torrcExample:
```
Hidden Service BTC RPC Explorer
HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ```
~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links:
- Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002
- LND: https://github.com/bitcoin/bitcoin/issues/28499
More info:
- https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/
- https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 16:56:24
@ b17fccdf:b7211155
2025-01-21 16:56:24It turns out that Ubuntu Linux installations of Ubuntu 23.04, 22.04.3 LTS, and installs done since April 2023 that accepted the Snap version update haven't been following Ubuntu's own recommended security best practices for their security pocket configuration for packages.
A new Subiquity release was issued to fix this problem while those on affected Ubuntu systems already installed are recommended to manually edit their
/etc/apt/sources.listfile.If you didn't install MiniBolt recently, you are affected by this bug, and we need to fix that manually if not we want to install all since cero. Anyway, if you installed Minibolt recently, we recommend you review that.
Follow these easy steps to review and fix this:
- Edit the
sources-listfile:
sudo nano /etc/apt/sources.list- Search now for every line that includes '-security' (without quotes) (normally at the end of the file) and change the URL to --> http://security.ubuntu.com/ubuntu
~ > For example, from http://es.archive.ubuntu.com/ubuntu (or the extension corresponding to your country) to --> http://security.ubuntu.com/ubuntu
~> Real case, Spain location, before fix:
``` deb http://es.archive.ubuntu.com/ubuntu jammy-security main restricted
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security main restricted
deb http://es.archive.ubuntu.com/ubuntu jammy-security universe
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security universe
deb http://es.archive.ubuntu.com/ubuntu jammy-security multiverse
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security multiverse
```
After fix:
``` deb http://security.ubuntu.com/ubuntu jammy-security main restricted
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security main restricted
deb http://security.ubuntu.com/ubuntu jammy-security universe
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security universe
deb http://security.ubuntu.com/ubuntu jammy-security multiverse
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security multiverse
```
Save and exit
Note: If you have already these lines changed, you are not affected by this bug, and is not necessary to do anything. Simply exit the editor by doing Ctrl-X
- Finally, type the next command to refresh the repository pointers:
sudo apt update- And optionally take the opportunity to update the system by doing:
sudo apt full-upgradeMore context:
- https://wiki.ubuntu.com/SecurityTeam/FAQ#What_repositories_and_pockets_should_I_use_to_make_sure_my_systems_are_up_to_date.3F
- https://bugs.launchpad.net/subiquity/+bug/2033977
- https://www.phoronix.com/news/Ubuntu-Security-Pocket-Issue
- Edit the
-
 @ b17fccdf:b7211155
2025-01-21 16:49:27
@ b17fccdf:b7211155
2025-01-21 16:49:27What's changed
- New method for Bitcoin Core signature check, click ~ >HERE< ~
- GitHub repo of Bitcoin Core release attestations (Guix), click ~ >HERE< ~
History:
~ > PR that caused the broken and obsolescence of the old signature verification process, click ~ >HERE< ~
~ > New GitHub folder of Bitcoin Core repo that stores the signatures, click ~ >HERE< ~
Thanks to nostr:npub1gzuushllat7pet0ccv9yuhygvc8ldeyhrgxuwg744dn5khnpk3gs3ea5ds for building the command that made magic possible 🧙♂️🧡
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 16:40:01
@ b17fccdf:b7211155
2025-01-21 16:40:01Important notice to MiniBolt node runners:
~ > It turns out that the I2P devs have opened an issue on the Bitcoin Core GitHub repo commenting that because they gave the option to enable the
notransit=trueparameter in the official documentation:[...] If you prefer not to relay any public I2P traffic and only allow I2P traffic from programs connecting through the SAM proxy, e.g. Bitcoin Core, you can set the no transit option to true [...] are having a heavy load on the I2P network since last December 19. Also comment that it is advisable to share as much bandwidth and transit tunnels as we can, to increase anonymity with coverage traffic, by contributing more to the I2p network than we consume.
So they ask that we deactivate that option that you use activated. With all this, he already updated the "Privacy" section by removing that setting.
The steps to delete this configuration once we have already configured it, are the following:
- With the "admin" user, stop i2pd:
sudo systemctl stop i2pd- Comment line 93 with "#" at the beginning of it (notransit = true), save and exit
sudo nano /var/lib/i2pd/i2pd.conf --line numbers- Start i2pd again:
sudo systemctl start i2pd- And that's it, you could take a look at Bitcoin Core to see that it has detected i2pd running again after the reboot with:
tail --lines 500 -f /home/bitcoin/.bitcoin/debug.log~ > If you don't see that I2P is up in Bitcoin Core after the restart,
sudo systemctl restart bitcoindand look again at the logs of the same.
More info in the rollback commit, see ~> HERE < ~
-
 @ b17fccdf:b7211155
2025-01-21 16:30:11
@ b17fccdf:b7211155
2025-01-21 16:30:11Your MiniBolt is on a home local network, you want to expose it on the public Internet (clearnet) without exposing your public IP, without Firewall rules, without NAT port forwarding, without risk, easy and cheap?
Go to the bonus guide by clicking ~ >HERE <~
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 16:23:44
@ b17fccdf:b7211155
2025-01-21 16:23:44Build your nostr relay step by step on your MiniBolt node! (easily adaptable to other environment) No need to trust anyone else! Be sovereign!
~> Go to the bonus guide by clicking ~> HERE< ~
~> This guide includes a complete extra section to cover the different processes for using nostr as a user and relay operator.
PS: The MiniBolt project has its FREE relay, be free to connect by adding to your favorite client the next address:
wss://relay.minibolt.info~> Let a review on noStrudel or Coracle of your experience using it.
Remember, Nostr is freedom! Stay resilient! 💜 🛡️💪
-
 @ b17fccdf:b7211155
2025-01-21 16:15:51
@ b17fccdf:b7211155
2025-01-21 16:15:51What's changed
A bonus guide to get a quick overview of the system status with the most relevant data about the services on the main guide.
➕Additional extra sections (optional) to:
- Show on login
- Get the channel.db size of an old LND bbolt database backend
- Use MobaXterm compatibility version
🔧 GitHub PR related: https://github.com/minibolt-guide/minibolt/pull/97
Σ Dedicated GitHub repository: https://github.com/minibolt-guide/system_overview
🫂Acknowledgments
This is a fork of the minibolt_info repository, the main developer of this project is rmnscb, a member of the MiniBolt community, all the merits go to him. Thank you for your contribution 🧡🫂
-> CLICK HERE <- to go to the bonus guide
Enjoy it MiniBolter! 💙
-
 @ 2f4550b0:95f20096
2025-01-21 16:06:18
@ 2f4550b0:95f20096
2025-01-21 16:06:18In the realm of leadership, whether in business, politics, or any organizational context, one of the most critical skills a leader can possess is the ability to make and keep promises. This skill not only builds trust and credibility, but also sets the tone for an organization's culture and operational ethos. A recent example of this leadership attribute can be observed in the actions of President Donald Trump on the first day of his second presidency, where he used executive orders to fulfill several campaign promises.
The Importance of Promises in Leadership
Leadership is fundamentally about influence, and one of the most effective ways to influence is through the power of your word. When leaders make promises, they are essentially laying down expectations for what stakeholders, customers, and employees can anticipate. These promises shape perceptions, motivate teams, and guide organizational strategy. However, the true test of leadership comes not in the making of these promises, but in their fulfillment.
Translating Promises into Action
On January 20, 2025, President Trump exemplified this principle by signing a flurry of executive orders that directly addressed several key campaign promises. These actions highlighted his approach to leadership. For instance, Trump signed executive actions on immigration, reversing many policies of his predecessor and reinstating his first-term policies like the "Remain in Mexico" initiative. This move was a direct fulfillment of his promise to tighten border control, demonstrating to his supporters and critics alike that his commitments were not merely rhetorical (https://www.whitehouse.gov/presidential-actions/2025/01/guaranteeing-the-states-protection-against-invasion/).
The Impact on Stakeholders
For stakeholders, the fulfillment of promises builds a reputation for reliability and decisiveness, essential for maintaining trust and support. From a leadership perspective, Trump's example underscores the importance of clarity in communication and the readiness to act on stated objectives.
Lessons for Leaders
Here are some key takeaways for leaders across sectors:
- Transparency: Be clear about what you promise. Ambiguity can lead to misunderstanding and disillusionment.
- Accountability: Hold yourself accountable. Demonstrate accountability to your promises.
- Action: Follow through with action. Leaders must not only talk the talk but walk the walk.
- Consistency: Maintain consistency between what you say and what you do. This builds a reliable brand or leadership image, whether in politics or business.
In conclusion, the skill of making and keeping promises is central to effective leadership. Promises are not just words; they are commitments that, when fulfilled, can define a leader's legacy and influence.
-
 @ 04c195f1:3329a1da
2025-01-21 16:04:39
@ 04c195f1:3329a1da
2025-01-21 16:04:39Dear Readers,
I’ve written about the AI Act before—you can read my full critique here—but now, parts of this bureaucratic monstrosity are about to become reality. Starting February 2, it will be illegal to use AI tools at work in the EU unless you can prove you have something called “AI competence.”
Let’s break this down.
What Does ‘AI Competence’ Mean?
No one knows. The EU has issued no practical guidance on how to define, evaluate, or measure this so-called competence. Yet, if you or your employees fail to meet this vague requirement, Brussels will be ready with the fines: up to €7 million or 1.5% of your company’s global revenue.
This is classic EU policymaking. Sweeping, unclear rules that businesses are left scrambling to interpret, while bureaucrats pat themselves on the back for ‘leading the way’ in AI regulation.
Who Does This Hurt Most?
Small and medium-sized businesses, naturally. These are the companies least equipped to deal with vague mandates or pay for the training programs that might, possibly, meet the requirements.
Meanwhile, big corporations will either move operations outside the EU or use their armies of lawyers to sidestep the rules entirely. The EU talks about fairness, but its policies always end up crushing the little guy while big players get a pass.
The Bigger Picture
AI is supposed to be the future. But while the US and China are racing ahead, the EU is busy tying businesses in regulatory knots. Is it any wonder that Europe is falling behind in innovation?
This isn’t just bad for business; it’s a direct assault on sovereignty and national economies. Instead of letting countries tailor AI policies to their needs, the EU insists on centralizing everything. The result? Fewer startups, fewer breakthroughs, and a Europe that’s increasingly irrelevant in global tech.
The Fight Ahead
February 2 is just the start. The full AI Act rolls out in stages, with more draconian measures to come. If we don’t push back now, this regulatory nightmare will only get worse.
National governments must reclaim control over AI policy before it’s too late. Europe’s future shouldn’t be dictated by unelected bureaucrats in Brussels.
What Do You Think?
How will these new rules impact Europe’s businesses and innovation? Reply to this read or shoot me a private message on Nostr.
Together, we can shine a light on the EU’s overreach and fight for a Europe that values sovereignty and innovation over red tape.
Stay informed, \ Dan Eriksson
-
 @ e3168078:10f13b2c
2025-01-21 15:44:45
@ e3168078:10f13b2c
2025-01-21 15:44:45ノス!
最近Umbrel上のn8nを使ってstacker newsの記事を要約するNostr botを作ってみました。
その際にFirecrawlというスクレイピングのSaaSを使っていたんですがセルフホストできるようなので試してみました。
Firecrawlは動的なページも読めたりマークダウンへの変換をしてくれますが無料プランだと1ヶ月500ページの制限があり、セルフホストすれば気兼ねなく使えます!
今回はUmbrel上のPortainerというアプリを使ってFirecrawlを動かせたのでその記録です。手順
まずはUmbrelにPortainerアプリをインストールします。 Poratinerは今回初めて使ったんですが独自のDockerコンテナをUmbrelで動かす際に推奨されているアプリのようです。

アプリを開いてパスワードの初期設定などを済ませるとダッシュボードが表示されるかと思います。 ここでStackという機能を使ってFirecrawlのDocker composeを一括で取り込むことができます。
新しいStackを作成する画面で以下を入力します。
Repository URL: https://github.com/mendableai/firecrawl
Repository reference: refs/heads/main
Compose path: docker-compose.yaml (デフォルトがymlになっててハマりました…)
上記に加えてenv varを設定する必要があるんですがPortainerでは上記の画像下部にあるように "Load Variables from .env file" からenvファイルを選択できます。 Firecrawlのgithubにあるように apps/api/.env.example をダウンロードし以下の内容を更新しPortainerに取り込ませます。
USE_DB_AUTHENTICATION=false TEST_API_KEY=fc-test-keyあとはDeploy the stackを押して少し待つとfirecrawlのセットアップ完了です。
確認
動作テストにはUmbrelの設定からAdvanced Settings -> Terminal -> Umbrel OSを開き以下のコマンドを実行ししマークダウンが返って来れば成功です。
$ curl -X POST http://localhost:3002/v1/scrape -H 'Authorization: Bearer fc-test-key' -H 'Content-Type: application/json' -d '{ "url": "https://example.com", "formats": ["markdown"] }' {"success":true,"data":{"markdown":"Example Domain\n==============\n\nThis domain is for use in illustrative examples in documents. You may use this domain in literature without prior coordination or asking for permission.\n\n[More information...](https://www.iana.org/domains/example)","metadata":{"title":"Example Domain","ogLocaleAlternate":[],"scrapeId":"7c196348-6561-4ebb-bb8a-9121a29c64b5","viewport":"width=device-width, initial-scale=1","sourceURL":"https://example.com","url":"https://example.com/","statusCode":200}}}またn8n等のUmbrelの他のアプリ(コンテナ)から利用する場合はlocalhostがコンテナ自身になってしまうので別のIP等(172.17.0.1)を使う必要があるのでご注意ください。 (参考)
以上でUmbrel上でのFirecrawlセルフホストができるようになりn8nからも制限なく使えるようになりました。
-
 @ 3ac03011:41ecd1bb
2025-01-21 13:56:58
@ 3ac03011:41ecd1bb
2025-01-21 13:56:58You've got to hand it to Trump. For centuries, politicians have hidden their corruption behind polite words like 'lobbying' and 'campaign donations.' But what happens when one leader decides to skip the facade entirely?
Enter $TRUMP: the grandaddy of all shitcoins—so brazen, so unapologetically self-serving, it's almost poetic. Why bother with the elaborate charade of influence-peddling when you can just mint a digital token and say, "Buy this if you want something from me"?
Need a policy changed? Pump $TRUMP. Want a ban lifted? You know the drill. Forget the subtle dance of lobbying—just load your wallet and fund your favour directly. It's simple. Efficient. And honestly, kind of genius if you have no morals.
The game has been the same: politicians selling out the people while posing as their saviours. They make soaring speeches, they shake hands, they kiss babies—and then they hand over the real power to the highest bidder. But at least they had the decency to keep up the illusion of caring. Trump? He's stripped away the illusion entirely.
Sure, it's a scam. But it's the most honest scam we've ever seen. No pretense. No empty promises about "making America great again." Just cold, hard transparency: "I'm for sale and now there's a token to prove it."
And really, isn't this just the logical endpoint of politics? Lobbying has always been bribery in a nice suit. Campaign donations? Legal pay-to-play. Trump just cut through the pageantry and put it on a blockchain.
Some will call it dystopian. But isn't it refreshing to see the grift so out in the open? The man is cutting out the middleman and embracing the essence of what leadership has become. Forget the speeches. Forget the empty promises. With $TRUMP, you don't need to wonder who he's working for—the market decides.
So here's to $TRUMP: the most honest scam in modern history. Maybe it's time for every politician to mint their own token—at least then we'd know exactly what they stand for. The audacity alone deserves respect.
[Image by Eric Fischl]
-
 @ c8cf63be:86691cfe
2025-01-21 13:48:28
@ c8cf63be:86691cfe
2025-01-21 13:48:28Das SNAFU des Reichtums
Das SNAFU-Prinzip[1] sagt das Kommunikation nur unter gleichen möglich ist:
Adäquate Kommunikation fliesst nur zwischen Gleichen ungehindert. Kommunikation zwischen Nicht-Gleichen ist missverständlich und von Dominaz- und Unterwerfungsritualen gefärbt, die immer wieder zum Zusammenbruch der Kommunikation führen und zu einem Spiel ohne Ende. [2]
So ist z. B. das Peter Prinzip [3] eine einfache Folge des SNAFU-Prinzips. Bezieht es sich in erster Linie auf Hierarchie lässt es sich hervorragend ausweiten auf den ökonomischen Bereich. Auch hier gilt, dass Kommunikation nur unter Gleichen möglich ist, hier ist die Hierarchie das ökonomische Ungleichgewicht.
Kommunikation ist auch hier nur unter gleichen möglich, ungefähr gleich reich müssen sie sein. Ein zu großer Unterschied in den ökonomischen Verhältnissen verhindert den Aufbau einer menschlichen Beziehung. Hier ist das einfache Beispiel: Wäre ich Reich, würde ich mich Fragen, ob die Freunde da, nur kommen weil ich ihnen die Drinks ausgebe. Jeder, der nicht so viel Geld wie ich hat, will vielleicht nur mein Geld. So kann ein Bill Gates nur einen Jeff Besos als Freund haben oder treffender ein Elon Musk nur einen Mark Zuckerberg.
Auch umgekehrt funktioniert diese Selektion: Wenn ich ein richtig cooler Typ wäre, würde ich mich fragen, ob ich den Reichen eigentlich gut finde, oder nur mit ihm rumhänge, weil er die Drinks bezahlt und weil ich zu Recht unsicher darüber sein kann, kann ich mich nur entziehen. Diejenigen, die wirklich freundschaftlich sind, sind die die sich einer solchen Situation nicht aussetzen.
Und was bleibt dem Reichen? Nur die Gesellschaft der Reichen. Hier trifft der Reichtum auf eine totale Armut. Die Auswahl der Freunde ist sehr klein.
Hier ist tatsächlich der Reichtum das Problem, bzw. das ökonomische Ungleichgewicht und es gibt eine einfache Lösung, der Unterschied muss kleiner werden, denn je kleiner der Unterschied desto mehr Auswahl an Freunden gibt es. Wie in der “Aufgeklärten Ökonomie” dargestellt ist die Ungleichheit, eine gesellschaftliche Entscheidung und eine konkrete Steuerung möglich. Wir können also den Reichen helfen und mehr Freiheit und Freunde schenken.
Pathologisch wird dieses Phänomen, wenn sich der innere Antrieb um den Reichtum dreht. Was durch die momentane Verfasstheit der gesellschaftlichen Praktiken sogar unterstützt und gefördert wird und damit viele Menschen objektiv unglücklich macht. Dieses pathologische der Gesellschaft wirkt dann auf das Individuum zurück und macht es ebenfalls Krank. Wir haben einen ähnlichen Mechanismus in der Gewalt kennenlernen dürfen. Vgl. “Gewalt ist eine ansteckende Krankrankheit”[https://cdn.satellite.earth/ac54bd400867c63f14e151172422067dc1b19980b1e738a577ae6c7a6ea835ea.png])
Wenn sie sich leer fühlen, Erfolg ihnen kein Glück schenkt, keine Befriedigung. Wenn sie mehr brauchen und mehr, dann leiden sie wahrscheinlich auch an einer Dysfunktion der Belohnungssysteme, an Habsucht.
Auch ihnen kann und muss geholfen werden, denn Gier ist heilbar. Und ihrer Gier betrifft nicht nur sie. Ihre liebsten Menschen in Ihrer Umgebung, Menschen mit denen sie niemals direkt in Berührung kommen, sie alle leiden unter ihrer Krankheit.
Auch für sie kann es ein erfülltes Leben geben, einen Weg zurück in die Gesellschaft, die Gesellschaft von Menschen. Machen sie Psychotherapie, nehmen sie Pharmaka, buchen sie eine Kur und entledigen sich ihres Wohlstandes.[4]
References:
[1] Wikipedia, SNAFU: https://de.wikipedia.org/wiki/SNAFU.
[2] Wilson, R.A., Der Neue Prometheus. Die Evolution unserer Intelligenz. - Volksausgabe/ Raubdruck. 1983. Seite 245-246
[3] Wikipedia, Peter Prinzip: https://de.wikipedia.org/wiki/Peter-Prinzip.
[4] InvestmentWeek, Sucht im Luxus: Eine Nacht in der Klinik der Superreichen 2024: https://www.investmentweek.com/sucht-im-luxus-eine-nacht-in-der-klinik-der-superreichen/, „Viele Patienten hier leiden an Einsamkeit“ … “Viele Superreiche …wüssten nicht, ob sie wegen ihres Geldes oder ihrer Persönlichkeit gemocht werden” „Reich sein bedeutet oft, keinen echten Kontakt zu haben. Viele unserer Klienten haben keine echten Freunde.“
-
 @ a012dc82:6458a70d
2025-01-21 13:47:17
@ a012dc82:6458a70d
2025-01-21 13:47:17In the annals of treasure hunting, tales of sunken galleons and buried chests have given way to a new narrative—one that unfolds in the digital realm. The U.S. Government, traditionally associated with the physical might of gold reserves in Fort Knox, has inadvertently entered the arena of cryptocurrency by amassing a staggering $5 billion in Bitcoin. This digital fortune, however, was not amassed through investment or mining efforts but rather through the seizure of assets from the darker corners of the internet. As we stand at the crossroads of finance and technology, this cache of Bitcoin opens up a Pandora's box of possibilities and challenges that could redefine the economic landscape of tomorrow.
Table Of Content
-
A Digital Fort Knox
-
The Origins of the Cache
-
The Dilemma of Liquidation
-
Potential Paths Forward
-
The Impact on the Future of Currency
-
Conclusion
-
FAQs
A Digital Fort Knox
Imagine a vault, not of steel and stone, but of complex cryptographic algorithms, housing a vast sum of Bitcoin equivalent to the wealth of small nations. This digital Fort Knox does not require armed guards or thick walls but instead relies on the impenetrable nature of blockchain technology. The U.S. Government's acquisition of such a significant amount of Bitcoin is a testament to the changing nature of value and wealth in the 21st century. Each Bitcoin in this modern trove was once part of illicit transactions, flowing through the veins of the internet until it was intercepted by the vigilant efforts of federal agencies. The narrative of each coin is a digital ledger, chronicling a journey from the shadowy fringes of the web to the secure wallets of the government.
The Origins of the Cache
The backstory of the government's Bitcoin collection is not one of serendipity but of strategic cyber sleuthing and legal might. It is a modern saga of law enforcement adapting to the challenges posed by the digital age. Federal agencies, armed with court orders and cutting-edge technology, have traced the movement of these digital assets through the blockchain, unraveling complex webs of transactions that lead to the criminal enterprises operating in the darknet markets. Each seizure represents a battle won in the ongoing war against cybercrime, with the confiscated Bitcoin serving as both evidence of victory and the spoils of war.
The Dilemma of Liquidation
The government's Bitcoin cache presents a unique conundrum: to liquidate or not to liquidate? This decision is fraught with economic implications, akin to a game of high-stakes poker where the government's hand could influence the entire table. A sudden influx of $5 billion worth of Bitcoin into the market could trigger a tidal wave of volatility, potentially devaluing the currency and destabilizing the fragile ecosystem of digital assets. The government must navigate these waters with a blend of economic savvy and strategic foresight, ensuring that any decision made is in the best interest of not just the immediate financial landscape but also the long-term viability of cryptocurrencies.
Potential Paths Forward
The government stands at the helm, charting a course through uncharted waters with its Bitcoin bounty. The options are as varied as they are complex. Holding onto the Bitcoin could be seen as an endorsement of its value, a digital reserve akin to the gold of yesteryear. Alternatively, a measured approach to selling the Bitcoin could be employed, releasing it into the market in a controlled manner to mitigate any negative impacts. There's also the innovative possibility of integrating Bitcoin into the government's financial transactions, embracing the very currency that was once shunned by the establishment.
The Impact on the Future of Currency
The U.S. Government's handling of this Bitcoin cache is not merely a financial decision; it is a statement on the future of currency itself. As the line between digital and fiat currencies blurs, the actions taken with this Bitcoin hoard could send ripples across the global economy. It could influence how governments around the world perceive and interact with digital assets, potentially ushering in a new era where cryptocurrency becomes a staple of economic policy and international trade.
Conclusion
The U.S. Government's Bitcoin cache is more than a collection of digital assets; it is a symbol of a new era in governance and economic strategy. The decisions made regarding this treasure will likely resonate through the annals of financial history, setting precedents for how nations interact with the burgeoning realm of digital currencies. As we delve deeper into this narrative, we realize that this treasure is not hidden but in plain sight, waiting to unlock a future where digital assets are as commonplace and as valuable as the gold once stored in the vaults of old.
FAQs
How did the U.S. Government acquire $5 billion in Bitcoin? The U.S. Government seized this Bitcoin from various cybercriminal operations and darknet markets through legal and technological efforts by federal agencies.
What is the significance of the government holding such a large amount of Bitcoin? This significant holding of Bitcoin by the government underscores the changing landscape of value and wealth, highlighting the increasing relevance of digital currencies in today's economy.
What challenges does the government face with this Bitcoin cache? The government faces the challenge of deciding how to manage and potentially liquidate the Bitcoin without causing market disruption due to the currency's volatility.
What are the potential strategies for the U.S. Government's Bitcoin cache? Strategies include holding the Bitcoin as a reserve asset, selling it off gradually to minimize market impact, or using it for government transactions and policy-making.
How could the government's handling of the Bitcoin cache affect the future of currency? The government's approach to managing the Bitcoin cache could set a precedent for how digital assets are treated by national entities, potentially influencing the integration of cryptocurrencies into mainstream finance.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ e8a4bb8b:05f739c6
2025-01-21 13:05:10
@ e8a4bb8b:05f739c6
2025-01-21 13:05:10Opinion about CoinUnited.io - Crypto Wallet (iphone)
⚠️ WARNING: CoinUnited.io is a SCAM ⚠️ Do NOT use CoinUnited.io for cryptocurrency trading or investments. Here's why: Hong Kong SFC Alert: Listed as a suspicious platform on July 25, 20241. Withdrawal Issues: Many users report being unable to withdraw funds12. Fake Trading Environment: Platform likely uses simulated trading, not real market transactions1. False Regulatory Claims: Makes unverified claims about regulatory compliance12. Ongoing Investigations: Currently under investigation by Hong Kong police5. User Complaints: Numerous reports of lost investments and blocked accounts26. Deceptive Practices: Uses high APRs and leverage to lure investors12. Protect yourself and others. Avoid CoinUnited.io at all costs. If you've invested, seek immediate assistance from financial authorities. Always verify the legitimacy of crypto platforms before investing. Stay safe and share this warning to prevent others from falling victim to this scam.
WalletScrutiny #nostrOpinion
-
 @ 16d11430:61640947
2025-01-21 12:21:41
@ 16d11430:61640947
2025-01-21 12:21:41Hark, yon travellers, and gather round, for I shall tell thee a tale most grievous and yet queer, of the Black Knights of Sydney and their wretched deeds. In the land where the sun doth ever blaze and the sand kisseth the seas at Manly and Bondi alike, there rose a brood of shadowy lords, clad not in chain nor plate, but in ill-gotten power and tongues oiled with guile. These knights, though mighty in posture, were naught but fraudsters, lording o’er their glass castles with tools of torment and tormentors loyal yet weary.
The Black Knights and Their Tools of Torture
In their domains of steel and enchantment, the Black Knights kept the lower folk—Outsiders and plebs alike—beneath their boots, using tools most cruel. Chief amongst these instruments was the Rack of Review, a devilish device to which all Outsiders were summoned come every quarter moon. Here, the Knights would scry their scrolls of "metrics" and "outputs," their eyes narrowing as they spoke vile proclamations:
"Thy deliverables are tardy, thy productivity meagre, and thy enthusiasm fit for the dunghill!"
Strapped metaphorically to the Rack, the poor sods would be stretched—not in limb but in labour, their hours extended without mercy, until naught but a husk remained.
The Gantt Wheel of Doom
Lo, there was also the Gantt Wheel, a terrible, spinning contraption upon which the timelines of the kingdom were writ. The Wheel turned ever faster as the Knights demanded projects be completed "on the morrow" or "ere the next new moon." The Outsiders, desperate to keep pace, toiled day and night, only to find their efforts scoffed at and their souls ground into dust beneath the Wheel’s ceaseless spin.
The Slack Shackles
But even in their rare moments of respite, the Outsiders were bound by the Slack Shackles, cursed chains that buzzed and hummed without end. Messages did flow through these infernal devices, demanding updates, meetings, and “quick chats” at all hours. Ne’er a dawn nor dusk passed without the Shackles tightening their grip, leaving their victims weary and witless.
The Documentation Dungeon
When a fresh Outsider entered the kingdom, they were hurled into the dreaded Documentation Dungeon, a chaotic cavern where ancient scrolls lay piled high, each more incomprehensible than the last. “Figure it out!” barked the Trusty Squires, those harried managers who served the Knights with reluctant fervour. And so the Outsiders wandered the Dungeon’s depths, driven mad by its riddles, while the Squires hurried off to tend to their younglings or steal a quiet moment of peace.
The Outsiders’ Plight
Amongst the many Outsiders was one of particular ambition, newly arrived from lands far beyond the kingdom. Full of ideas and burning with determination, this Outsider sought not merely survival, but to reshape the very kingdom itself. Yet their brilliance was met with scorn, their ideas brushed aside by the Squires, whose refrain was always the same:
"Aye, 'tis a good idea, but I’ve no time for thee."
The Black Knights, meanwhile, saw in the Outsider not potential, but peril. "This one dares to shine too brightly," they muttered. "We must see them humbled."
The Reckoning
It came to pass that the Outsider, weary of the endless grind, began to see the cracks in the Knights’ armour. They discovered that the Rack’s metrics were flawed, the Gantt Wheel’s spin could be slowed, and the Slack Shackles could be hacked. Sharing their findings with their fellow Outsiders, they sowed the seeds of rebellion.
The Trusty Squires, long burdened by their double lives as enforcers and reluctant parents, began to waver. "Perhaps," they whispered, "the Outsiders speak true." And so, one by one, the Squires laid down their scrolls and joined the cause.
When the day of reckoning came, the Outsiders and their allies turned the Knights’ tools against them. The Rack, once a symbol of shame, now displayed the Knights’ own failings for all to see. The Gantt Wheel ground to a halt, and the Slack Shackles shattered into silence.
The Knights, their power undone, fled to their glass castles, clutching at their dwindling authority. The Outsiders, meanwhile, seized the kingdom, dismantling the tools of oppression and forging a new order where all could thrive.
A New Order
And so it was that the land of Sydney was reborn, no longer ruled by the Black Knights, but by a council of equals. The Rack was transformed into a table of collaboration, the Gantt Wheel into a tool of fairness, and the Shackles into oaths of trust. The Documentation Dungeon was cleared and made into a grand library, where knowledge was shared freely.
As for the Black Knights, their names faded from memory, their castles left to crumble. And the Outsiders, once strangers in a strange land, became the stewards of a kingdom built not on fear, but on hope.
And lo, the folk of Sydney lived happily, though ever wary of the shadows where new knights might rise. For they had learned a hard truth: that tyranny doth thrive where ambition goes unguarded, and freedom must ever be defended, even on the golden shores of Manly.
-
 @ da0b9bc3:4e30a4a9
2025-01-21 10:13:52
@ da0b9bc3:4e30a4a9
2025-01-21 10:13:52Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/858364
-
 @ 16d11430:61640947
2025-01-21 09:07:27
@ 16d11430:61640947
2025-01-21 09:07:27In the modern world, human existence often feels like a series of transactions. Our labor, emotions, and even our identities are bought, sold, and traded in systems that shape how we live and think. From the workplace to the digital economy, commodification—the transformation of people and their qualities into marketable goods—is a driving force. To explore this, we can draw a provocative yet insightful parallel between corporations, brothels, and the psychological toll of commodifying the self.
The Nature of Commodification
Commodification begins when something intrinsic, like human labor, creativity, or even intimacy, is turned into a product to be exchanged. This process is not inherently negative; it has enabled trade, specialization, and economies of scale. However, when commodification extends to the very essence of human life, it can distort how we view ourselves and others.
In corporations, employees are reduced to "human resources," evaluated for their productivity and cost-effectiveness.
In brothels, intimacy—a deeply personal and emotional act—is transformed into a service exchanged for money.
Both systems, while different in form and function, rely on similar transactional mechanics that highlight the tension between value creation and value extraction.
The Psychological Impact of Transactional Systems
When humans are commodified, a subtle but profound psychological shift occurs. The person begins to see themselves and others as products or tools, rather than as complex, multifaceted beings. This can lead to:
- Alienation from the Self
In corporations, workers may feel disconnected from the fruits of their labor, performing tasks that serve abstract goals (like shareholder profits) rather than personal or communal fulfillment.
In brothels, commodifying intimacy can create a dissonance between personal emotions and professional detachment.
- Reductionism in Identity
Both systems reduce individuals to specific roles: the "employee" or the "service provider." This narrow definition can strip away the richer dimensions of identity, leading to feelings of inadequacy or loss of purpose.
The language used—whether "key performance indicators" in corporations or "clients and services" in brothels—reinforces this reductionism.
- Emotional Transactionalism
When human relationships are repeatedly framed in transactional terms, individuals may struggle to form connections based on trust and reciprocity. Instead, they might view all interactions as exchanges of value, weakening the bonds of empathy and community.
Corporations and Brothels: Ethical and Unethical Dimensions
To fully understand the parallels, it’s important to acknowledge the spectrum of ethical possibilities within these systems. Both corporations and brothels can operate in ways that empower or exploit, depending on their structure, governance, and priorities.
Exploitation: When Systems Extract Value
In corporations, employees may feel like cogs in a machine, with minimal control over their work or compensation. Performance metrics, layoffs, and rigid hierarchies often amplify feelings of disposability.
In brothels, particularly those in unregulated or exploitative settings, workers may experience coercion, unsafe conditions, and a lack of autonomy over their lives.
Empowerment: When Systems Create Value
Ethical corporations foster creativity, collaboration, and meaningful contributions, treating employees as partners in a shared mission rather than mere labor inputs.
Progressive brothels, when regulated and consensual, can provide safe spaces for individuals to exercise autonomy, set boundaries, and earn a livelihood on their terms.
The key distinction lies in the balance between value creation and extraction, agency and coercion, empowerment and exploitation.
The Bitcoin Perspective: A Model for Fair Systems
Bitcoin offers a lens through which to critique commodification and envision systems that respect human agency and dignity. Unlike traditional corporations or centralized institutions, Bitcoin operates as a decentralized, transparent network where value is exchanged without middlemen or coercion. Its principles of proof of work, immutability, and voluntary participation provide a counterpoint to the exploitative tendencies of fiat systems.
- Transparency and Accountability
In Bitcoin, every transaction is recorded on a public ledger, ensuring that no entity can obscure or manipulate value flows.
Similarly, corporations and brothels could adopt transparent governance models, where stakeholders—whether workers, customers, or clients—can verify fairness and accountability.
- Agency and Sovereignty
Bitcoin restores financial control to individuals, allowing them to participate in the economy on their terms.
Ethical corporations and brothels should likewise empower individuals with choices and the ability to set their terms of participation.
- Value Without Exploitation
Bitcoin’s decentralized system eliminates the need for exploitative intermediaries. Applying this principle, organizations could prioritize equitable value exchange, ensuring that no one is reduced to a disposable asset.
Healing the Psychological Impact
To move beyond the psychological toll of commodification, societies must reimagine systems of work and exchange. This involves:
- Redefining Value
Value should extend beyond monetary metrics to include well-being, relationships, and personal growth. Organizations must recognize that human worth cannot be quantified.
- Restoring Meaning
Work and services, whether in corporations or brothels, should align with personal values and societal benefits. This creates a sense of purpose and connection.
- Fostering Empathy
Recognizing the humanity of everyone involved in a system—whether coworkers, clients, or customers—helps rebuild trust and compassion.
Conclusion: A New Paradigm for Transactional Systems
The metaphor of corporations as brothels is not about judgment but about understanding how transactional systems shape our psychology and relationships. By examining these parallels, we can challenge the commodification of the self and advocate for systems that prioritize human dignity, agency, and fairness.
Bitcoin, as a decentralized, transparent alternative, offers a glimpse of what such systems could look like. It challenges us to move beyond extraction and exploitation, toward value exchange that respects the complexity of human life. In doing so, it invites us to create a world where transactions do not diminish us but empower us to live fully and authentically.
-
 @ dbb19ae0:c3f22d5a
2025-01-21 09:00:36
@ dbb19ae0:c3f22d5a
2025-01-21 09:00:36Warning: Use this at your own risk Backup your files before using them in the software Backup often, test your backup. Verify and dry test your files before doing a production run
I had to write this program because rmdir was claiming not to have enough authorization
context nostr:note1l0u4pw5xp73eultr9nf5tgmlsgnv9q05wdqha4t6grd4699v74zssshm40
```perl use strict; use warnings; use File::Path qw(remove_tree);
Specify the directory to be deleted
my $directory = 'c:\Users\mydirectory\mysubdirectory\';
Remove the directory
remove_tree($directory, {error => \my $err});
Check for errors
if (@$err) { foreach my $diag (@$err) { my ($file, $message) = %$diag; if ($file eq '') { print "General error: $message\n"; } else { print "Problem unlinking $file: $message\n"; } } } else { print "Directory successfully deleted.\n"; }
```
-
 @ 16d11430:61640947
2025-01-21 08:17:01
@ 16d11430:61640947
2025-01-21 08:17:01Corporate infidelity—the betrayal of principles, trust, or ethics for personal or organizational gain—breeds a toxic "cheat culture" that often promotes cheaters to the highest ranks. This phenomenon undermines meritocracy, rewards unethical behavior, and creates a cycle where deception becomes normalized. Here's an exploration of how this happens, supported by evidence and psychoanalysis of the relationship between cheaters and corporate leadership.
- How Corporate Infidelity Breeds a Cheat Culture
Corporate infidelity sets a precedent that unethical behavior is acceptable if it delivers results. Over time, this shapes an organizational culture where:
-
Cheating Becomes a Norm: When employees see unethical practices rewarded or ignored, they learn that integrity is secondary to success.
-
Survival of the Craftiest: In such cultures, those who can manipulate systems, cut corners, or deceive stakeholders often rise faster than those adhering to principles.
-
Erosion of Accountability: A lack of accountability fosters a permissive environment, where leaders themselves engage in and benefit from unethical practices.
- Evidence of Cheat Culture in Leadership
Several high-profile scandals illustrate how cheating has propelled individuals to leadership positions:
Wells Fargo Fake Accounts Scandal
What Happened: Thousands of employees, pressured by unrealistic sales targets, created millions of unauthorized customer accounts.
Leadership's Role: Senior executives not only incentivized this behavior but ignored warnings from whistleblowers.
Outcome: The culture of cheating started at the top, as leaders prioritized growth over ethics, and they faced only minimal accountability initially.
Theranos and Elizabeth Holmes
What Happened: Elizabeth Holmes, the founder of Theranos, misrepresented the capabilities of her company’s blood-testing technology to investors and regulators.
Leadership Dynamics: Holmes created a culture where employees were pressured to meet impossible expectations, even if it meant falsifying results.
Outcome: Holmes’s rise was fueled by her charisma and ability to sell a dream, despite the underlying fraud.
Enron and Skilling’s Leadership
What Happened: Enron executives engaged in widespread accounting fraud to inflate profits and conceal debt.
Leadership’s Role: CEO Jeffrey Skilling cultivated a high-pressure environment that rewarded financial manipulation and punished transparency.
Outcome: Enron’s collapse highlighted how cheat culture at the top devastates entire organizations.
- Psychoanalysis: The Relationship Between Cheaters and Corporate Leadership
The relationship between cheaters and corporate leadership is symbiotic, driven by psychological and organizational factors:
A. Psychological Traits of Cheaters in Leadership
- Narcissism: Many corporate cheaters possess narcissistic traits, including an inflated sense of self-importance and a lack of empathy. They manipulate others to maintain their power and image.
Example: Elizabeth Holmes’s portrayal as a visionary leader allowed her to deflect scrutiny for years.
- Risk-Taking Behavior: Cheaters often thrive in environments where calculated risk-taking is rewarded, pushing boundaries until ethical lines are crossed.
Example: Enron executives’ risky financial strategies were initially celebrated as innovative.
- Machiavellianism: A tendency to prioritize personal gain over principles enables cheaters to navigate corporate politics and manipulate others.
Example: Executives at Volkswagen during the Dieselgate scandal prioritized market dominance over compliance.
B. Why Organizations Promote Cheaters
-
Results-Oriented Metrics: Companies often measure success by short-term outcomes (e.g., profits, growth) rather than long-term sustainability. Cheaters excel at delivering impressive metrics, even if through unethical means.
-
Fear and Obedience: Cheaters in leadership roles cultivate a culture of fear, discouraging dissent and ensuring compliance with their unethical practices.
-
Halo Effect: Charismatic cheaters, like Elizabeth Holmes or Jeffrey Skilling, use their charm and vision to distract from ethical shortcomings, earning trust from boards and investors.
-
Cultural Blind Spots: Organizations with weak ethical frameworks or poor governance fail to detect or address unethical behavior until it’s too late.
- The Long-Term Impact of Cheat Culture
The systemic promotion of cheaters to leadership has far-reaching consequences:
-
Erosion of Trust: Employees, investors, and customers lose faith in organizations when scandals come to light.
-
Demoralization of Ethical Employees: High-performing, ethical employees are often overlooked or pushed out, leading to talent attrition.
-
Reinforced Cycle of Corruption: When cheaters rise to power, they perpetuate a culture that rewards unethical behavior, creating a self-sustaining system.
-
Breaking the Cycle: Preventing Cheat Culture
-
Transparent Governance: Implementing decentralized systems like blockchain can provide immutable records of decisions and transactions, reducing opportunities for manipulation.
-
Ethical Leadership Training: Developing leaders with strong ethical foundations ensures accountability at the top.
-
Whistleblower Protections: Encouraging employees to report unethical practices without fear of retaliation can help identify and address issues early.
-
Focus on Long-Term Metrics: Shifting from short-term profits to long-term value creation reduces pressure to cheat.
-
Adopting Bitcoin Principles: Bitcoin’s trustless, decentralized nature eliminates reliance on charismatic but untrustworthy individuals, promoting accountability.
Conclusion
Corporate infidelity fosters a cheat culture where unethical behavior is rewarded and cheaters rise to the top. This dynamic is fueled by psychological traits like narcissism and organizational flaws such as results-oriented metrics and weak governance. High-profile scandals, from Theranos to Enron, illustrate the dangers of such cultures. However, with transparent systems, ethical leadership, and decentralized accountability mechanisms like Bitcoin, organizations can break this cycle and rebuild trust, integrity, and fairness in corporate leadership.
-
 @ 16d11430:61640947
2025-01-21 07:59:13
@ 16d11430:61640947
2025-01-21 07:59:13Corporate infidelity—marked by ethical breaches, dishonesty, and the prioritization of profits over principles—has plagued modern society. From environmental scandals to financial fraud, these betrayals erode trust, destabilize economies, and perpetuate inequality. However, the emergence of Bitcoin and its underlying blockchain technology presents a transformative solution. With its emphasis on transparency, decentralization, and immutability, Bitcoin offers a path to ending corporate infidelity and its widespread societal effects.
The Roots of Corporate Infidelity
Corporate infidelity thrives in centralized systems that lack accountability and incentivize short-term gains. Whether it's manipulating emissions data, exploiting customer trust, or undermining environmental stewardship, these actions are enabled by opaque structures, fiat-based incentives, and unchecked power.
Key Factors Enabling Corporate Infidelity:
-
Opaque Financial Systems: Fiat-based systems rely on centralized control, allowing manipulation, fraud, and mismanagement to go unchecked.
-
Short-Termism: Quarterly earnings reports and profit-driven motives often override long-term ethical commitments.
-
Lack of Transparency: Traditional corporate governance operates behind closed doors, making it difficult to identify and address misconduct.
-
Centralized Power: Concentrated authority within organizations enables unethical behavior to persist unchecked.
How Bitcoin and Blockchain Combat Corporate Infidelity
Bitcoin, as a decentralized, transparent, and immutable financial system, addresses the structural weaknesses that enable corporate infidelity. Here’s how:
- Immutable Transparency
Bitcoin’s blockchain is a public ledger where all transactions are permanently recorded and verifiable. This transparency makes it nearly impossible to manipulate financial data or hide unethical practices.
Impact on Corporate Governance: By integrating blockchain technology, companies can create verifiable records of financial transactions, supply chains, and decision-making processes, reducing opportunities for fraud and corruption.
- Decentralized Accountability
Bitcoin operates without central authority, redistributing power to a global network of participants. This decentralization reduces the risks of concentrated decision-making that often lead to unethical behavior.
Impact on Corporations: Decentralized systems empower stakeholders—employees, customers, and investors—to hold corporations accountable. Transparent decision-making eliminates the "black box" of traditional corporate governance.
- Alignment of Incentives
Bitcoin’s protocol incentivizes long-term participation and trust. Its deflationary nature discourages reckless monetary expansion, aligning with sustainable practices over speculative short-term gains.
Impact on Society: Corporations operating on Bitcoin-based systems are encouraged to prioritize stability and value creation, reducing the focus on quarterly profits at the expense of ethics.
- Smart Contracts and Automation
Blockchain-enabled smart contracts enforce agreements automatically without intermediaries. These contracts can ensure compliance with ethical and operational standards, removing the possibility of infidelity.
Example Use Case: Companies can automate ethical practices, such as verifying supply chain sustainability or ensuring fair wages, through immutable smart contracts.
- Trustless Systems
Bitcoin eliminates the need for trust in third parties by relying on cryptographic proof. This trustless design reduces opportunities for betrayal and infidelity within corporate structures.
Impact on Employees and Customers: With verifiable systems in place, stakeholders no longer need to rely on promises—they can verify outcomes independently.
Real-World Applications: Bitcoin in Action
- Supply Chain Transparency
Blockchain-based systems allow for end-to-end tracking of goods, ensuring ethical sourcing and eliminating fraud. Companies like IBM are already leveraging blockchain for supply chain transparency.
- Financial Integrity
Bitcoin eliminates the need for centralized banks and financial intermediaries, reducing risks of financial mismanagement. Companies can integrate Bitcoin payments to promote transparency in financial transactions.
- Decentralized Audits
Blockchain-based auditing ensures that financial reports are accurate and tamper-proof, making it harder for corporations to engage in fraudulent activities.
Transforming Society Through Bitcoin
The societal benefits of Bitcoin extend beyond the corporate world. By addressing corporate infidelity, Bitcoin can help create a more equitable, sustainable, and trustworthy society:
- Restoring Trust in Institutions
Bitcoin’s emphasis on transparency and accountability can rebuild public trust in corporations, governments, and financial systems.
- Promoting Ethical Leadership
Leaders operating in Bitcoin-based systems are incentivized to act ethically, as their actions are subject to public scrutiny.
- Reducing Inequality
By decentralizing power and removing intermediaries, Bitcoin empowers individuals and small businesses, reducing wealth concentration and systemic inequality.
- Accelerating Justice
Immutable records on the blockchain can expedite legal and regulatory processes, ensuring swift accountability for unethical behavior.
Challenges and the Road Ahead
While Bitcoin offers a powerful tool for combating corporate infidelity, its adoption faces challenges, including regulatory resistance, technical literacy gaps, and cultural inertia. To fully realize its potential:
-
Education and Advocacy: Stakeholders must understand Bitcoin’s capabilities and embrace its principles.
-
Policy Integration: Governments and organizations need to develop frameworks that encourage blockchain adoption.
-
Cultural Shift: A commitment to transparency, accountability, and decentralization must become a societal norm.
Conclusion
Corporate infidelity has long undermined trust, stability, and equality in society. Bitcoin offers a revolutionary alternative, providing the means and methods to end unethical practices through transparency, decentralization, and accountability. By embracing Bitcoin’s principles, corporations and societies can foster a future built on trust, integrity, and sustainable value creation—a future where betrayal of principles is no longer an option.
-
-
 @ 5579d5c0:db104ded
2025-01-21 07:07:21
@ 5579d5c0:db104ded
2025-01-21 07:07:21When it comes to metabolic health, most conversations revolve around nutrition (low-carb, keto, low-fat, calories in calories out etc.) and exercise.
While these are undeniably important, they only address part of the picture.
The real elephant in the room is often overlooked: circadian health.
This fundamental aspect of biology underpins metabolic function and is the key driver of dysfunction when disrupted.

Circadian Health: The Missing Piece
Your body operates on a 24-hour clock in line with the rising and setting of the sun.
This natural cycle, called the circadian rhythm, regulates critical functions like sleep, energy production, hormone release, and digestion.
Every cell in your body has its own internal clock, working together to coordinate metabolism and energy production.
Circadian rhythm disruption is the invisible force driving metabolic dysfunction.
Lack of morning sunlight and regular light exposure throughout the day, paired with excessive artificial light at night and blue light, throws the system into chaos.
Add misaligned eating habits, such as eating late at night, and you have the perfect recipe for metabolic dysfunction.
But how does circadian rhythm disruption lead to metabolic dysfunction?
A good question.
The circadian clock governs the rhythmic release of hormones, and synchronises metabolic processes with daily light-dark cycles.
Let’s start with Leptin.
Leptin is a hormone produced by fat cells that signals to the brain how much energy your body has.
When Leptin levels are low, you feel hungry, and the body conserves energy.
When Leptin levels are high, you feel full, and the body is more likely to use fat for energy.
Leptin levels naturally follow a circadian rhythm, peaking at night to signal energy sufficiency and promote fat-burning during sleep.
When circadian rhythms are disrupted, the brain stops responding properly to Leptin signals, leading to Leptin resistance, which causes to increased hunger, fat storage, and reduced fat burning, even when Leptin levels are high.
If you’re overweight or have a waist-to-height ratio over 0.5, you are most likely Leptin resistant.

Next up, Insulin
Insulin is naturally released by the pancreas in response to rising blood sugar levels, typically after eating, to help cells absorb glucose (sugar) for energy or storage.
Insulin sensitivity is naturally highest in the morning and decreases in the evening.
Disruption of circadian rhythms in the pancreas impairs Insulin secretion, leading to higher blood glucose levels.
Simultaneously, circadian misalignment reduces the responsiveness of muscle, liver, and fat cells to Insulin, promoting hyperinsulinemia (higher levels of Insulin).
Over time, this dysregulation leads to Insulin resistance, setting the stage for metabolic dysfunction, namely Type 2 Diabetes.
Our stress hormone Cortisol is involved too.
Morning sunlight is critical for maintaining the body’s natural Cortisol rhythm, which kickstarts metabolic activity for the day.
Elevated night time Cortisol, a hallmark of circadian disruption, impairs Leptin signalling, raises blood glucose, while further desensitising cells to Insulin.

And finally, Melatonin, yes your sleep hormone.**
Melatonin levels should be higher at night and lower in the morning.
Cortisol suppresses the brains ability to release Melatonin, disrupting sleep and circadian alignment further.
Reduced Melatonin levels exacerbates Leptin resistance and promotes fat storage, particularly visceral fat.
So when we add all these up we have weight gain, raised blood sugar, visceral fat deposition, blunted fat burning and high Cortisol, a recipe for metabolic health disaster.
Fixing your circadian health
Where do you start?
- Morning sunlight: Exposing yourself to natural light within 30 minutes of waking helps synchronise your circadian clock. This simple habit improves Leptin sensitivity, Cortisol rhythms, and overall metabolic health.
- Sunlight exposure throughout the day: Take regular breaks to step outside for 5–10 minutes every 1–2 hours to anchor your circadian rhythm.
- Limit artificial light at night: Reducing exposure to screens and bright lights after sunset helps protect Melatonin production, supporting sleep and metabolic repair. Use dim, amber/red lighting and wear blue light-blocking glasses in the evening.
- Aligned eating window: Eating from sunrise to sunset, within a 10–12-hour window, no snacking, avoiding late-night meals to optimise insulin sensitivity and fat burning.
The bigger picture
Addressing metabolic health without considering light environment is like expecting flowers to bloom in the dark.
Nutrition and exercise matter, but without proper circadian alignment, the foundation of your metabolic health remains compromised.
By focusing on your light exposure, meal timing, and circadian rhythm, you will become more Leptin sensitive, Insulin regulation, and fat metabolism.
It’s not just about eating the right foods or doing the right workouts, it’s about living in sync with your body’s natural rhythm.
-Chris
If you are interested in working with me book a call here.
-
 @ 75656740:dbc8f92a
2025-01-21 04:38:21
@ 75656740:dbc8f92a
2025-01-21 04:38:21We spend too much time enthralled by even numbers. We can instantly tell if a number is even or odd and often have preferences in the matter. In grade school we memorize rules like
- An even plus an even is an even
- An odd plus an odd is an even
- An even plus an odd is and odd
And so forth to rules of multiplication. But this magical quality of numbers really just means evenly divisible by 2. What is so special about 2? Shouldn't we just as well care if a number is divisible by 3?
So I am introducing threeven numbers as all numbers divisible by 3.
0, 3, 6, 9, 12, 15, ...
are all threeven numbers. But what about numbers that aren't divisible by 3? Numbers that are not divisible 2 are called odd so I guess throdd?
There is, however, a slight problem. There seem to be more throdd numbers than threeven numbers.
1, 2, 4, 5, 7, 8, 10, 11, 13, 14, ...
To solve that we need to think about what an odd number is. If an even number is some number n times 2 or 2n then odd numbers are 2n + 1
This gives a nice way to think about threeven numbers as well. Every threeven is 3n and a throdd is 3n + 1 and we need to introduce throdder numbers as 3n + 2. There isn't any reason that there should only be two types of numbers. So instead of numbers that are divisible by 2 and numbers that aren't, we have numbers that are divisible by 3, numbers that are 1 greater than a multiple of three and numbers that are 2 greater than a multiple of three.
To recap
- Threeven = 3n
- Throdd = 3n + 1
- Throdder = 3n + 2
Now for handy rules of thumb.
- A threeven plus a threeven is a threeven
- A threeven plus a throdd is a throdd
- A threeven plus a throdder is a throdder
- A throdd plus a throdd is a throdder
- A throdd plus a throdder is a threeven
- A throdder plus a throdder is a throdd
And, for multiplication
- A threeven times a threeven is a threeven
- A threeven times a throdd is a threeven
- A threeven times a throdder is a threeven
- A throdd times a throdd is a throdd
- A throdd times a throdder is a throdder
- A throdder times a throdder is a throdd
This is just modular arithmetic and the same can be done for any integer n
m mod n = 0
Means m is an nven and there will be n - 1 varieties of nodd
Threeven, however, is the most fun to say and makes the point nicely, there is no need to carry it further.
Note: it appears that I am not the first to have discovered threeven numbers. And now you are stuck knowing about them as well.
-
 @ ed84ce10:cccf4c2a
2025-01-21 02:40:19
@ ed84ce10:cccf4c2a
2025-01-21 02:40:19Hackathon Summary
The HackSecret 4 hackathon brought together 130 developers to focus on developing decentralized confidential computing applications using the Secret Network. The event involved 48 projects, each utilizing Secret's Confidential Computing Layer and interfacing with blockchains such as Cosmos, EVM, and Solana. The hackathon was divided into two main tracks: Cross-Chain dApps and Native Secret dApps, both highlighting Secret's privacy features.
Structured support was provided through workshops on deploying dApps and confidential computing for environments such as EVM, IBC, and Solana. Developer resources supported participants in learning about Secret contracts, especially for newcomers. The prize pool totaled $12,000 USD, awarded in SCRT and SEI tokens. Some notable projects included confidential voting systems, sealed-bid auctions, and private voting mechanisms.
The hackathon emphasized technical innovation and practical problem-solving within the ecosystem of decentralized applications. Through active participation and creative submissions, the event contributed to expanding the Secret Network's ecosystem and promoted confidential computing advancements in Web3 technologies.
Hackathon Winners
7,000 SCRT Prize Winners
- Private Acknowledge Receipt: A blockchain system designed for confidential information sharing using NFTs with encrypted private data, ensuring secure data access and notifications on-chain.
- Great Walk NFT Experience: Connects hiking trails with NFTs that evolve as users progress, utilizing Secret Network for privacy and featuring a user-friendly frontend.
5,000 SCRT Prize Winners
- On-Chain 2FA: Integrates two-factor authentication via Google Authenticator for improved security in smart contracts and accounts on Secret Network.
- SecretHacks: A decentralized platform using vote encryption to ensure unbiased project evaluations for community funding and hackathons.
3,500 SCRT Prize Winners
- Straw Hat Builds: Supports developers moving from tutorial learning to real projects using blockchain and Rust, with an emphasis on practical application.
- KittyMix: A cat collecting game that encourages community-driven NFT remixing, leveraging Secret Network for hosting pixel-art NFTs with unique attributes.
2,000 SCRT Prize Winners
- Saffron - Escrow: Provides secure digital asset escrow services in the CosmWasm ecosystem, enhanced by Secret Network's privacy features for token and NFT trades.
- Secret Password Manager: A decentralized credential management system using Secret Network's confidential computing, offering a secure smart contract and web interface for credentials.
For a comprehensive overview of all projects, visit HackSecret 4 on DoraHacks.
About the Organizer
Secret Network
Secret Network is a blockchain platform that emphasizes data privacy and secure computation, distinguishing itself with privacy-preserving technologies. It enables encrypted smart contracts, offering enhanced data confidentiality compared to conventional blockchain systems. Initiatives include privacy-preserving DeFi applications and partnerships to expand privacy utilities within the blockchain ecosystem. The current mission of Secret Network is to advance privacy protections, build a more secure and decentralized web infrastructure, and empower developers and users with versatile privacy features.
-
 @ fbf0e434:e1be6a39
2025-01-21 02:40:10
@ fbf0e434:e1be6a39
2025-01-21 02:40:10Hackathon 回顾
HackSecret 4 Hackathon汇集了130位开发者,集中开发使用Secret Network的去中心化机密计算应用。活动涉及48个项目,每个项目都使用了Secret的机密计算层,并与诸如Cosmos、EVM和Solana等区块链进行交互。Hackathon分为两个主要赛道:跨链dApps和本地Secret dApps,两者都突出了Secret的隐私特性。
通过针对EVM、IBC和Solana等环境的dApps部署和机密计算的研讨会提供了结构化支持。开发者资源支持参与者学习Secret合约,特别是针对新手。奖池总额为12,000美元,以SCRT和SEI代币发放。一些值得注意的项目包括机密投票系统、密封投标拍卖和私人投票机制。
Hackathon强调了去中心化应用生态系统中的技术创新和实际问题解决能力。通过积极参与和创造性提交,活动为Secret Network生态系统扩展作出贡献,并促进了Web3技术中机密计算的进步。
Hackathon Winners
7,000 SCRT Prize Winners
- Private Acknowledge Receipt: 一个区块链系统,设计用于使用带有加密私密数据的NFT进行机密信息共享,确保在链上安全数据访问和通知。
- Great Walk NFT Experience: 将远足小径与随用户进展而演变的NFT连接起来,使用Secret Network实现隐私,并具有用户友好的前端界面。
5,000 SCRT Prize Winners
- On-Chain 2FA: 集成Google Authenticator的双因素认证,以提高Secret Network上智能合约和账户的安全性。
- SecretHacks: 一个去中心化平台,使用投票加密以确保社区资金和Hackathon项目评估时的不偏见。
3,500 SCRT Prize Winners
- Straw Hat Builds: 支持开发者从教程学习转向真实项目的开发,使用区块链和Rust,强调实际应用。
- KittyMix: 一个鼓励社区驱动型NFT重混的猫咪收集游戏,利用Secret Network托管具有独特属性的像素艺术NFT。
2,000 SCRT Prize Winners
- Saffron - Escrow: 提供CosmWasm生态系统中的安全数字资产托管服务,通过Secret Network的隐私特性增强代币和NFT交易。
- Secret Password Manager: 使用Secret Network的机密计算的去中心化凭证管理系统,提供安全的智能合约和凭证的网页界面。
欲了解所有项目的全面概述,请访问DoraHacks上的HackSecret 4。
关于组织者
Secret Network
Secret Network是一个专注于数据隐私和安全计算的区块链平台,以隐私保护技术为特点。它能够加密智能合约,提供比传统区块链系统更高的数据机密性。其举措包括隐私保护的DeFi应用,以及在区块链生态系统中扩展隐私功能的合作伙伴关系。Secret Network的当前使命是推进隐私保护,构建更安全和去中心化的网络基础设施,并通过多功能隐私功能赋能开发者和用户。
-
 @ 04ed2b8f:75be6756
2025-01-21 02:26:28
@ 04ed2b8f:75be6756
2025-01-21 02:26:28A warrior does not fear chaos—he thrives in it. Life is a battlefield, and disorder is the forge in which strength, strategy, and resilience are tempered. Whether in the pursuit of victory in business, relationships, or personal conquest, chaos is an inevitable adversary. But within every storm lies an opportunity—an opening to strike, to evolve, and to dominate where others falter. Only those who embrace the struggle with unwavering resolve can turn uncertainty into their greatest weapon.
Understanding Chaos
Chaos is not the enemy; it is the proving ground. It manifests as upheaval, setbacks, and unexpected challenges, forcing warriors to sharpen their minds and steel their resolve.
- Disruption Breeds Innovation: In the heat of battle, new tactics emerge. When the known paths are obliterated, new strategies take form.
- Mindset Is Your Strongest Weapon: Chaos can either crush you or forge you into something stronger. The choice lies within your perception.
- Growth Is Forged in Adversity: The greatest warriors are those who embrace discomfort, wielding it to forge endurance and ingenuity.Seizing Opportunity Amidst Chaos
- Adaptability Is Strength
-
The warrior who can shift tactics swiftly gains the upper hand. Flexibility and awareness allow for swift and decisive action where others hesitate.
-
Chaos Fuels Creativity
-
In the heat of turmoil, the boldest ideas are born. Warriors do not cling to old ways; they adapt, overcome, and conquer.
-
Endings Are Just New Battles
- What seems like defeat is often a call to arms for greater conquests. Every setback is a chance to regroup and strike back with renewed vigor.
Harnessing Chaos for Victory
- Remain Steady Amid the Storm: Fear clouds judgment; clarity is power. Observe, assess, and act with precision. Opportunities reveal themselves to those who master control over their emotions.
- Strike First, Strike Hard: Do not merely react to chaos—command it. Take decisive actions that position you ahead of the pack.
- Exploit Weaknesses: Where others see insurmountable problems, a warrior sees openings and opportunities to advance.
Lessons from the Battlefields of History
Legends are not born in times of peace but in the crucible of chaos. From generals who turned the tide of war in moments of despair to entrepreneurs who built empires from ruin, history is a testament to those who harnessed disorder and emerged victorious.
Conclusion: Chaos Is the Warrior's Ally
Chaos is not to be feared but embraced. It is the ultimate test of will and strategy. A true warrior sees beyond the disorder, crafting victory from the wreckage. In every crisis lies the seed of triumph; in every conflict, the chance to rise.
When chaos surrounds you, stand firm, sharpen your sword, and remember—opportunity belongs to those with the courage to seize it.
-
 @ 16d11430:61640947
2025-01-21 02:14:26
@ 16d11430:61640947
2025-01-21 02:14:26Part Two Of Series on Mastering the Musca
Building on the foundational physical conditioning required to catch a Musca domestica mid-flight, the second pillar of mastery lies in the cultivation of patience, refined visual tracking, and the perception of time. The process transcends physical agility, diving into cognitive and perceptual skills that are as much about mental discipline as they are about muscle memory.
The Science of Patience and Observation
Patience is the cornerstone of fly-catching excellence. Research in attentional control emphasizes that prolonged focus on erratic and unpredictable targets trains the brain's ability to maintain sustained attention. The ability to remain calm and observant under pressure—waiting for the opportune moment to act—relies on the prefrontal cortex, which governs impulse control and decision-making.
This form of patience, often described in meditative practices, lowers cortisol levels and enhances neuroplasticity, allowing individuals to adapt to the seemingly chaotic flight patterns of flies. Athletes in this discipline develop an intuitive understanding of when to strike, a skill honed through repetitive practice and exposure to unpredictable stimuli.
Visual Tracking: Decoding the Fly’s Erratic Patterns
Flies exhibit highly unpredictable movements, characterized by abrupt shifts in speed and direction. This erratic trajectory, driven by their compound eyes and rapid wing beats, challenges the human visual system. Successful fly-catching requires the athlete to excel in smooth-pursuit eye movements and saccades, which are rapid eye movements that recalibrate focus on moving targets.
Studies in visual-motor integration highlight that tracking small, fast-moving objects enhances neural efficiency in the occipital and parietal lobes. These regions process spatial information and coordinate motor responses. High-level performers develop an acute ability to anticipate trajectories by identifying subtle cues in the fly’s movement, such as wing positioning or changes in velocity.
Predictive Timing and the Illusion of "Slowing Down Time"
One of the most remarkable phenomena in fly-catching is the perception of slowed time during critical moments. This effect, documented in high-performance sports and combat scenarios, is attributed to the brain's increased processing of sensory input during periods of heightened arousal. By compressing time through rapid neural computations, the brain allows individuals to act with extraordinary precision.
Predictive timing, governed by the cerebellum, is essential for this process. The cerebellum calculates the fly’s likely trajectory, enabling the hand to intercept the target even as it changes direction. Repeated practice strengthens the cerebellar circuits, creating a feedback loop that enhances accuracy and reaction speed.
Refining the Craft Through Research
Prominent studies in neuroscience and sports science provide insights into training methods for aspiring fly-catching athletes:
-
Dynamic Visual Acuity Training: Exercises such as tracking moving dots on a screen can improve the ability to focus on fast-moving objects.
-
Anticipatory Drills: Practicing with simulated erratic targets, such as drones or programmable devices, hones the predictive capabilities of the brain.
-
Mindfulness and Reaction Time: Meditation and mindfulness training have been shown to reduce reaction times by calming the nervous system and improving attentional focus.
-
Eye-Hand Coordination Tools: Devices like stroboscopic glasses create controlled visual disruptions, forcing the brain to adapt to incomplete information.
The Path to Mastery
The art of fly-catching merges the physical, cognitive, and perceptual domains into a singular skill set. Through rigorous training, practitioners learn to read the chaotic dance of the fly, anticipate its movements, and act with surgical precision. The process demands patience, discipline, and a commitment to understanding the intricate connection between body and mind.
As Australia continues to explore this unique and challenging sport, its athletes embody a profound lesson: true mastery is not merely about speed or strength but the harmony of mind and body in the face of chaos.
-
-
 @ 30b99916:3cc6e3fe
2025-01-21 02:08:26
@ 30b99916:3cc6e3fe
2025-01-21 02:08:26Details
- 🍳 Cook time: 10 to 8 minutes at 350
- 🍽️ Servings: About 4 dozen cookies
Ingredients
- 2 sticks of butter
- 2 eggs
- 1 cup granulated sugar
- 1 cup brown sugar
- 1 cup peanut butter
- 1 t vanilla
- 2 cups flour
- 1/2 t salt
- 1 t soda
- 6 oz Semi-Sweet Chocolate chips (optional)
Directions
- Blend butter, eggs, vanilla and sugars together thoroughly
- Next blend in peanut butter thoroughly
- Next blend in flour, salt, and soda thoroughly
- Optional blend in chocolate chips
- Add about table spoon of cookie dough per cookie on a cookie sheet. With a fork based in sugar place a cross hatch pattern on each cookie. Bake cookies for 10 to 8 minutes and place onto cooler rack.
-
 @ 16d11430:61640947
2025-01-21 01:57:53
@ 16d11430:61640947
2025-01-21 01:57:53The Lightning Network (LN), a layer-2 protocol designed to scale Bitcoin transactions, is a powerful innovation that combines the reliability of Bitcoin's blockchain with the speed and affordability of off-chain payment channels. For node operators, the Lightning Network represents more than just a technical endeavor; it is a gateway to reimagining global finance and fostering economic empowerment. Here, we’ll delve into the motivations, responsibilities, and ambitions of Lightning Network node operators in today’s rapidly evolving ecosystem.
The Role of a Node Operator
At its core, a Lightning Network node operator is a steward of Bitcoin's second layer. By running a node, operators help facilitate instant, low-cost payments across the network. These nodes act as routing hubs, allowing users to send payments without directly opening a channel with one another.
But being a node operator is more than maintaining a server. It requires careful channel management, liquidity provisioning, and routing efficiency. A well-managed node contributes to the overall health and capacity of the Lightning Network, making it more reliable and accessible.
Ambitions Driving Node Operators
-
Decentralized Financial Sovereignty Many operators are motivated by the vision of a decentralized financial future. By running a node, they actively participate in building a trustless and permissionless payment network. This aligns with Bitcoin's ethos of financial sovereignty, where users can transact freely without intermediaries.
-
Earning Yield on Bitcoin Holdings Lightning Network node operators can earn routing fees by efficiently managing payment channels. While these fees are modest compared to traditional investments, they provide a way to earn yield on Bitcoin holdings without surrendering custody or relying on centralized services.
-
Enhancing Network Resilience A robust and well-distributed network is essential for Bitcoin's long-term success. Node operators aim to enhance the resilience of the Lightning Network by ensuring sufficient liquidity and efficient routing, especially in underserved regions.
-
Promoting Bitcoin Adoption Lightning Network enables microtransactions and instant payments, making Bitcoin more practical for everyday use. Node operators see themselves as enablers of this adoption, supporting merchants, applications, and users by providing reliable payment infrastructure.
-
Exploring Business Opportunities Beyond fees, the Lightning Network opens up new business models. From hosting custodial wallets to offering Lightning-as-a-Service (LaaS) for developers, node operators are at the forefront of experimenting with innovative monetization strategies.
Challenges in the Path of Ambition
Running a Lightning Network node is not without its hurdles. Operators face several challenges:
Liquidity Management: Balancing inbound and outbound liquidity is critical. Mismanagement can lead to failed transactions or idle capital.
Technical Expertise: Operating a node requires knowledge of Bitcoin, LN protocols, and server infrastructure, making it less accessible for non-technical users.
Competition: As the network grows, efficient routing and competitive fees become essential for attracting traffic.
Regulatory Uncertainty: In some jurisdictions, the role of node operators in financial systems remains ambiguous, potentially exposing them to legal scrutiny.
Current Implementations and Innovations
The Lightning Network ecosystem has evolved rapidly, offering tools and services to support node operators:
-
Node Management Tools: Platforms like ThunderHub, Ride the Lightning (RTL), and Amboss provide user-friendly interfaces for managing nodes and channels.
-
Liquidity Services: Services like Lightning Pool and Voltage help operators source liquidity, improving their routing capabilities.
-
Privacy Enhancements: Protocol upgrades like BOLT-12 aim to improve privacy for both users and operators, protecting transaction metadata.
-
Cross-Chain Applications: Some node operators are exploring integrations with other networks, enabling interoperability and expanding the use cases for LN payments.
A Vision for the Future
The ambitions of Lightning Network node operators reflect the broader vision of a decentralized, equitable, and efficient global financial system. As the network grows, operators will play a pivotal role in shaping its trajectory, driving innovation, and ensuring accessibility.
From powering micropayments for digital content to enabling financial inclusion in underserved regions, the Lightning Network's potential is vast. And at the heart of this potential lies the dedication of node operators—custodians of Bitcoin's scalability and champions of its ethos.
The road ahead is both challenging and inspiring. For node operators, it is an opportunity to pioneer a new financial paradigm, one channel at a time.
-
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ 85cd42e2:0e6f2173
2025-01-20 22:49:02
@ 85cd42e2:0e6f2173
2025-01-20 22:49:02
Solomon, Moses, and Melchizedek were worshipping, and an enchanting beast was underneath the throne, and its mouth was an abyss. A cunning angel worshiped near the three prophets and said to them, "Any who can satisfy the Beast at the Lord's feet will be blessed forever." \ \ The three prophets spoke among themselves and asked the angel, "What is the beast's name?" \ \ And the angel answered them, "She is called ‘Desire’." \ \ Solomon went before the Beast and it spoke and said, "I can only be satisfied by great treasure." Solomon was a man of great riches, so he cast all his vast empire into the mouth of the Beast, but it was not filled. The Beast said, "What a marvelous offering! There are many great treasures, but something else is needed. You are blessed, but you shall go away empty-handed." Solomon was impoverished but rejoiced. \ \ Moses went before the Beast, and the Beast spoke and said, "Do you have great treasure?" Moses was a mighty prophet, so he struck the earth with his staff and made a river of gold flow into the mouth of the Beast for eternity, but it was not filled. The Beast spoke and said, "Moses, you are cursed to gaze until this river fills my belly." And Moses was cursed to gaze
upon the abyss that could not be filled until the end of the age. \ \ Melchizedek went before the Beast, and the Beast spoke and said, "No matter what I eat, I am not satisfied." Melchizedek said, "I see that if a man gives all he has, you are not satisfied. I see that if a man gives you treasures without meaning, it is the same as offering dust and you will curse him. Thus, I will give you a portion of a treasure that has great worth." Melchizedek had two jewels called Urim and Thummim. He gave the black stone to the Beast, and the Beast didn't desire to eat Urim without Thummim. She did not consume the jewel but gazed upon it and desired its pair. The Beast spoke and said, "Give me the other stone." Melchizedek replied, "If I give you the other, you will consume both and we will have nothing between us. Let us make a covenant; If you will not bless me or curse me, but let me live in peace, I will give you Thummim at the end of time." The Beast agreed to Melchizedek's request and fashioned Urim into an amulet, and that amulet became the only possession of the Beast called Desire. Thus, Melchizedek subdued Desire by teaching her that satisfaction is not in consumption, stockpiling, or might. Satisfaction is found in treasure shared between two souls.
#poetry #writing #bitcoin #literature #story #stories #mythology #books#readstr #grownostr #bookstr #fantasy #plebstr #readstr #philosophy#art #artst #family #parenting #plebianmarket #market #zap #diy#nostrart #hodl #proofofwork #craft #artisans #nashville #market #olas#artwork #digitalart #buyintoart #dadlife #smallbusiness #education#kidsbook #gift #gm #artist #introductions #wisdom
-
 @ 50809a53:e091f164
2025-01-20 22:30:01
@ 50809a53:e091f164
2025-01-20 22:30:01For starters, anyone who is interested in curating and managing "notes, lists, bookmarks, kind-1 events, or other stuff" should watch this video:
https://youtu.be/XRpHIa-2XCE
Now, assuming you have watched it, I will proceed assuming you are aware of many of the applications that exist for a very similar purpose. I'll break them down further, following a similar trajectory in order of how I came across them, and a bit about my own path on this journey.
We'll start way back in the early 2000s, before Bitcoin existed. We had https://zim-wiki.org/
It is tried and true, and to this day stands to present an option for people looking for a very simple solution to a potentially complex problem. Zim-Wiki works. But it is limited.
Let's step into the realm of proprietary. Obsidian, Joplin, and LogSeq. The first two are entirely cloud-operative applications, with more of a focus on the true benefit of being a paid service. I will assume anyone reading this is capable of exploring the marketing of these applications, or trying their freemium product, to get a feeling for what they are capable of.
I bring up Obsidian because it is very crucial to understand the market placement of publication. We know social media handles the 'hosting' problem of publishing notes "and other stuff" by harvesting data and making deals with advertisers. But- what Obsidian has evolved to offer is a full service known as 'publish'. This means users can stay in the proprietary pipeline, "from thought to web." all for $8/mo.
See: https://obsidian.md/publish
THIS IS NOSTR'S PRIMARY COMPETITION. WE ARE HERE TO DISRUPT THIS MARKET, WITH NOTES AND OTHER STUFF. WITH RELAYS. WITH THE PROTOCOL.
Now, on to Joplin. I have never used this, because I opted to study the FOSS market and stayed free of any reliance on a paid solution. Many people like Joplin, and I gather the reason is because it has allowed itself to be flexible and good options that integrate with Joplin seems to provide good solutions for users who need that functionality. I see Nostr users recommending Joplin, so I felt it was worthwhile to mention as a case-study option. I myself need to investigate it more, but have found comfort in other solutions.
LogSeq - This is my "other solutions." It seems to be trapped in its proprietary web of funding and constraint. I use it because it turns my desktop into a power-house of note archival. But by using it- I AM TRAPPED TOO. This means LogSeq is by no means a working solution for Nostr users who want a long-term archival option.
But the trap is not a cage. It's merely a box. My notes can be exported to other applications with graphing and node-based information structure. Specifically, I can export these notes to:
- Text
- OPML
- HTML
- and, PNG, for whatever that is worth.
Let's try out the PNG option, just for fun. Here's an exported PNG of my "Games on Nostr" list, which has long been abandoned. I once decided to poll some CornyChat users to see what games they enjoyed- and I documented them in a LogSeq page for my own future reference. You can see it here:
https://i.postimg.cc/qMBPDTwr/image.png
This is a very simple example of how a single "page" or "list" in LogSeq can be multipurpose. It is a small list, with multiple "features" or variables at play. First, I have listed out a variety of complex games that might make sense with "multiplayer" identification that relies on our npubs or nip-05 addresses to aggregate user data. We can ALL imagine playing games like Tetris, Snake, or Catan together with our Nostr identities. But of course we are a long way from breaking into the video game market.
On a mostly irrelevant sidenote- you might notice in my example list, that I seem to be excited about a game called Dot.Hack. I discovered this small game on Itch.io and reached out to the developer on Twitter, in an attempt to purple-pill him, but moreso to inquire about his game. Unfortunately there was no response, even without mention of Nostr. Nonetheless, we pioneer on. You can try the game here: https://propuke.itch.io/planethack
So instead let's focus on the structure of "one working list." The middle section of this list is where I polled users, and simply listed out their suggestions. Of course we discussed these before I documented, so it is note a direct result of a poll, but actually a working interaction of poll results! This is crucial because it separates my list from the aggregated data, and implies its relevance/importance.
The final section of this ONE list- is the beginnings of where I conceptually connect nostr with video game functionality. You can look at this as the beginning of a new graph, which would be "Video Game Operability With Nostr".
These three sections make up one concept within my brain. It exists in other users' brains too- but of course they are not as committed to the concept as myself- the one managing the communal discussion.
With LogSeq- I can grow and expand these lists. These lists can become graphs. Those graphs can become entire catalogues of information than can be shared across the web.
I can replicate this system with bookmarks, ideas, application design, shopping lists, LLM prompting, video/music playlists, friend lists, RELAY lists, the LIST goes ON forever!
So where does that lead us? I think it leads us to kind-1 events. We don't have much in the way of "kind-1 event managers" because most developers would agree that "storing kind-1 events locally" is.. at the very least, not so important. But it could be! If only a superapp existed that could interface seamlessly with nostr, yada yada.. we've heard it all before. We aren't getting a superapp before we have microapps. Basically this means frameworking the protocol before worrying about the all-in-one solution.
So this article will step away from the deep desire for a Nostr-enabled, Rust-built, FOSS, non-commercialized FREEDOM APP, that will exist one day, we hope.
Instead, we will focus on simple attempts of the past. I encourage others to chime in with their experience.
Zim-Wiki is foundational. The user constructs pages, and can then develop them into books.
LogSeq has the right idea- but is constrained in too many ways to prove to be a working solution at this time. However, it is very much worth experimenting with, and investigating, and modelling ourselves after.
https://workflowy.com/ is next on our list. This is great for users who think LogSeq is too complex. They "just want simple notes." Get a taste with WorkFlowy. You will understand why LogSeq is powerful if you see value in WF.
I am writing this article in favor of a redesign of LogSeq to be compatible with Nostr. I have been drafting the idea since before Nostr existed- and with Nostr I truly believe it will be possible. So, I will stop to thank everyone who has made Nostr what it is today. I wouldn't be publishing this without you!
One app I need to investigate more is Zettlr. I will mention it here for others to either discuss or investigate, as it is also mentioned some in the video I opened with. https://www.zettlr.com/
On my path to finding Nostr, before its inception, was a service called Deta.Space. This was an interesting project, not entirely unique or original, but completely fresh and very beginner-friendly. DETA WAS AN AWESOME CLOUD OS. And we could still design a form of Nostr ecosystem that is managed in this way. But, what we have now is excellent, and going forward I only see "additional" or supplemental.
Along the timeline, Deta sunsetted their Space service and launched https://deta.surf/
You might notice they advertise that "This is the future of bookmarks."
I have to wonder if perhaps I got through to them that bookmarking was what their ecosystem could empower. While I have not tried Surf, it looks interested, but does not seem to address what I found most valuable about Deta.Space: https://webcrate.app/
WebCrate was an early bookmarking client for Deta.Space which was likely their most popular application. What was amazing about WebCrate was that it delivered "simple bookmarking." At one point I decided to migrate my bookmarks from other apps, like Pocket and WorkFlowy, into WebCrate.
This ended up being an awful decision, because WebCrate is no longer being developed. However, to much credit of Deta.Space, my WebCrate instance is still running and completely functional. I have since migrated what I deem important into a local LogSeq graph, so my bookmarks are safe. But, the development of WebCrate is note.
WebCrate did not provide a working directory of crates. All creates were contained within a single-level directory. Essentially there were no layers. Just collections of links. This isn't enough for any user to effectively manage their catalogue of notes. With some pressure, I did encourage the German developer to flesh out a form of tagging, which did alleviate the problem to some extent. But as we see with Surf, they have pioneered in another direction.
That brings us back to Nostr. Where can we look for the best solution? There simply isn't one yet. But, we can look at some other options for inspiration.
HedgeDoc: https://hedgedoc.org/
I am eager for someone to fork HedgeDoc and employ Nostr sign-in. This is a small step toward managing information together within the Nostr ecosystem. I will attempt this myself eventually, if no one else does, but I am prioritizing my development in this way:
- A nostr client that allows the cataloguing and management of relays locally.
- A LogSeq alternative with Nostr interoperability.
- HedgeDoc + Nostr is #3 on my list, despite being the easiest option.
Check out HedgeDoc 2.0 if you have any interest in a cooperative Markdown experience on Nostr: https://docs.hedgedoc.dev/
Now, this article should catch up all of my dearest followers, and idols, to where I stand with "bookmarking, note-taking, list-making, kind-1 event management, frameworking, and so on..."
Where it leads us to, is what's possible. Let's take a look at what's possible, once we forego ALL OF THE PROPRIETARY WEB'S BEST OPTIONS:
https://denizaydemir.org/
https://denizaydemir.org/graph/how-logseq-should-build-a-world-knowledge-graph/
https://subconscious.network/
Nostr is even inspired by much of the history that has gone into information management systems. nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn I know looks up to Gordon Brander, just as I do. You can read his articles here: https://substack.com/@gordonbrander and they are very much worth reading! Also, I could note that the original version of Highlighter by nostr:npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft was also inspired partially by WorkFlowy.
About a year ago, I was mesmerized coming across SubText and thinking I had finally found the answer Nostr might even be looking for. But, for now I will just suggest that others read the Readme.md on the SubText Gtihub, as well as articles by Brander.
Good luck everyone. I am here to work with ANYONE who is interested in these type of solution on Nostr.
My first order of business in this space is to spearhead a community of npubs who share this goal. Everyone who is interested in note-taking or list-making or bookmarking is welcome to join. I have created an INVITE-ONLY relay for this very purpose, and anyone is welcome to reach out if they wish to be added to the whitelist. It should be freely readable in the near future, if it is not already, but for now will remain a closed-to-post community to preemptively mitigate attack or spam. Please reach out to me if you wish to join the relay. https://logstr.mycelium.social/
With this article, I hope people will investigate and explore the options available. We have lots of ground to cover, but all of the right resources and manpower to do so. Godspeed, Nostr.
Nostr #Notes #OtherStuff #LogSec #Joplin #Obsidian