-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 2b24a1fa:17750f64
2025-04-19 14:02:59
@ 2b24a1fa:17750f64
2025-04-19 14:02:59Jeder kann heute eine beliebige Identität annehmen, egal welches Geschlecht oder welche Tiergattung. Eine Identität soll zukünftig allerdings nicht mehr zur Disposition stehen: die digitale.
https://soundcloud.com/radiomuenchen/in-die-digitalisierung-gezwungen-von-norbert-haring?
So droht der Koalitionsvertrag unmissverständlich: „Jeder Bürger und jede Bürgerin erhält verpflichtend ein Bürgerkonto und eine digitale Identität.“ Diese Zwangsbeglückung mag auf den ersten Blick harmlos erscheinen. Mit Blick über den großen Teich aber, bekommen wir einen Vorgeschmack auf das potenzielle Ungemach einer solchen e-ID.
Norbert Häring zeichnet das Szenario, das uns in Deutschland mit der obligatorischen e-ID ins Haus steht.
Hören Sie seinen Text „In die Digitalität gezwungen“, nachzulesen auf seinem Blog:
norberthaering.de/new/sozialversicherungsnummer/
Sprecher: Karsten Tryoke
Bild: KI
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 4cebd4f5:0ac3ed15
2025-04-19 13:52:54
@ 4cebd4f5:0ac3ed15
2025-04-19 13:52:54Tóm tắt Hackathon
uOttaHack 7 – hackathon chính thức của Đại học Ottawa – thu hút 286 người tham gia và 138 dự án. Diễn ra từ ngày 17–19/1/2025, sự kiện tập trung vào tiêu chí đổi mới, độ phức tạp kỹ thuật, tính thực tiễn và khả năng trình bày, đảm bảo các giải pháp sáng tạo cho vấn đề thực tế.
Hackathon thúc đẩy hợp tác đa ngành, chào đón sinh viên mọi trình độ tham gia phát triển phần mềm và công nghệ tác động. Sự kiện nhấn mạnh học hỏi và kết nối, tạo cơ hội cho developer mới và có kinh nghiệm cùng phát triển kỹ năng. uOttaHack 7 phản ánh sứ mệnh của Đại học Ottawa trong thúc đẩy đổi mới, đồng thời ghi nhận dự án sáng tạo thể hiện kỹ năng kỹ thuật và tiềm năng ứng dụng thực tế.
Các dự án đoạt giải
uOttaHack 7 trao giải cho 23 hạng mục với 853 người tham gia. Dưới đây là những dự án tiêu biểu:
uOttaHack General Challenge Prize Winners
- KellerApp: Cầu nối giao tiếp giữa người nghe và khiếm thính qua công cụ dịch tiếng Anh sang ngôn ngữ ký hiệu (BSL).
- MemoryMate: Kính thông minh tích hợp AI hỗ trợ bệnh nhân sa sút trí nhớ gợi lại tương tác qua ứng dụng.
- Sweatris: Game Tetris tương tác điều khiển bằng chuyển động cơ thể, kết hợp thể dục và giải trí.
Solace Prize Winner
- uOttaType: Nâng cao cộng tác tài liệu với AI, bao gồm chuyển giọng nói thành văn bản và chat thời gian thực, sử dụng Solace Event Brokers.
QNX Prize Winner
- QNX - Traffic Lights: Hệ thống đèn giao thông thời gian thực triển khai trên Raspberry Pi 4 với QNX 8.0, tích hợp tính năng cho người đi bộ.
Survey Monkey Prize Winners
- Opinionated Orangutans: Tạo khảo sát cá nhân hóa bằng OpenAI APIs, phân tích thói quen duyệt web.
- Survey Monkey Chatbot: Thu thập dữ liệu khảo sát qua chatbot dùng GROQ AI và phân tích cảm xúc.
- Cartbuddy: Ứng dụng retail feedback tích hợp AI, sử dụng SurveyMonkey APIs.
NAV CANADA Prize Winner
DeepCode Prize Winner
- SecureVision: Hệ thống phân tích mối đe dọa bảo mật, nâng cấp dữ liệu thô thành insight nâng cao.
Starknet Prize Winners
- Dice-Roll OnChain: Game C++ trên blockchain Starknet với xác thực minh bạch.
- Playtopia: Build Your Game, Earn Real $$$: Nền tảng kiếm tiền qua game kỹ năng.
- Focusify | Distributed Mental Health Focus App: Ứng dụng tập trung học tập bằng cơ chế game hóa và công nghệ phi tập trung.
Gadget Prize Winners
- cuNext: Thiết kế lại giao diện Carleton Central để cải thiện trải nghiệm người dùng.
- Skej: Tạo lịch học bằng AI, tích hợp đánh giá giáo sư và điều khiển bằng giọng nói.
Groq Prize Winner
- SilentGuard: Ứng dụng cứu hộ khẩn cấp qua cuộc gọi giả và cụm từ kích hoạt, sử dụng AI.
MLH Prize Winners
- SecureVision, AgentSingularity (triển khai AI agent tùy chỉnh), KellerApp, Talent Forge (trao đổi kỹ năng phi tiền tệ), SilentGuard, Act2Learn (học tập qua kịch bản role-play).
Tail'ed Prize Winner
- HealthSync-360: Ứng dụng theo dõi sức khỏe tích hợp Groq AI, kế hoạch mở rộng với nền tảng thể thao lớn.
Chi tiết dự án tại uOttaHack 7 Projects.
Về Nhà tổ chức
uOttaHack
uOttaHack là đơn vị tổ chức hackathon và cộng đồng tập trung thúc đẩy đổi mới công nghệ, phát triển kỹ năng trong lĩnh vực blockchain và công nghệ. Với chuyên môn tổ chức sự kiện khuyến khích giải quyết vấn đề sáng tạo, uOttaHack xây dựng danh tiếng trong việc nuôi dưỡng tài năng kỹ thuật và tạo cơ hội kết nối. Định hướng hiện tại của tổ chức bao gồm thúc đẩy tiến bộ công nghệ và hỗ trợ dự án có tiềm năng tác động đến hệ sinh thái tech.
-
 @ 866e0139:6a9334e5
2025-04-19 13:37:37
@ 866e0139:6a9334e5
2025-04-19 13:37:37Autor: Mathias Bröckers. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
»Die meisten domestizierten Primaten auf Terra hatten keine Ahnung davon, dass sie Primaten waren. Sie hielten sich für etwas anderes und ›Besseres‹ als den Rest des Planeten. Selbst Benny Benedict ging in seiner Kolumne ›Noch einen Monat‹ davon aus. Benny hatte zwar Darwin gelesen, aber das war im College gewesen und schon eine Weile her. Er hatte dort auch von Wissenschaften wie Ethologie und Ökologie gehört, aber die Fakten der Evolution waren ihm nie richtig klar geworden. Er hielt sich keineswegs für einen Primaten und hatte auch noch nie bemerkt, dass seine Freunde und Bekannten welche waren. Vor allem erkannte er nicht, dass die Alphamännchen ... typische Anführer von Primatenbanden waren. Als Folge dieser Unfähigkeit, das Offensichtliche zu erkennen, war Benny ständig über sein eigenes Verhalten und das seiner Freunde, Bekannten und besonders der Alphamännchen bekümmert, manchmal sogar richtiggehend entsetzt. Weil er nicht wusste, dass dies ein ganz normales Primatenverhalten ist, erschien es ihm einfach s c h r e c k l i c h.«
Robert A. Wilson, Schrödingers Katze
Das Durchschnittsbewusstsein der domestizierten Primaten auf der Erde zeichnet sich unter anderem dadurch aus, dass es sich eine weder lebende noch tote Katze, mit der Erwin Schrödinger einst die Konsequenzen der Quantenphysik erklärte, nicht vorstellen kann. Koexistierende Zwischenzustände zwischen Dasein und Nicht-Dasein – sei es von Katzenkörpern oder von Atomteilchen – sind für den gemeinen Primatenverstand ein Unding, und so kommt es, dass auch 80 Jahre nach ihrer Entdeckung die Quantenrealität kaum wahrgenommen wird. Das kann nicht überraschen. Nicht einmal die fast 500 Jahre alte Entdeckung des Kopernikus ist in die semantischen Schaltkreise der Primatenhirne eingegangen: Bis heute reden sie davon, dass die Sonne »auf«- oder »unter«-geht. Wie tief diese Prägung ist, kann jede/r beim nächsten prächtigen Sonnenuntergang überprüfen: Es dauert einige Minuten, bis man sich klar gemacht hat und »spürt«, dass nicht die Sonne, sondern die Erde sich dreht.
Wann kommt unsere kopernikanische Wende?
Woran liegt es, dass unserem Bewusstsein auch nach einem halben Jahrtausend die kopernikanische Wende nicht implantiert ist? Robert Anton Wilson zufolge sind es die zwei ältesten und am tiefsten geprägten Schaltkreise des Primatenhirns – sie sichern Bio-Überleben und emotional-territorialen Ansprüche –, die den von Symbolen (Sprache) geprägten dritten Schaltkreis okkupieren. Dank dieses egozentrischen »Reptilienhirns«, wie Carl Sagan es nannte, empfinden domestizierte Primaten emotionalen oder territorialen Statusverlust als Bedrohung.
Jedes Alphamännchen kann den ganzen Primatenstamm hinter sich bringen, wenn es ihn überzeugt, dass es ein anderes Alphamännchen auf ihr Territorium abgesehen hat. Ist es gelungen, diesen »patriotischen« Schaltkreis anzuklicken und auch noch genügend Bio-Überlebensangst zu produzieren, handelt der Stamm nach Gedankensystemen, die einer rationalen Analyse keine fünf Minuten standhalten. Zwar werden die Anthropologen nicht müde, die vor etwa 11.000 Jahren entstandenen ersten Siedlungen der domestizierten Primaten als zivilisatorische Großleistung zu rühmen, schließlich hatten die einzelnen Alphamännchen noch kurz zuvor ihr Territorium mit Exkrementen abgesteckt und Eindringlinge mit diesen Grenzmarkierungen beworfen.
Doch wie wenig sich im Kern geändert hat, lässt sich an bestimmten Redewendungen ablesen. So ziehen bis heute die domestizierten Primaten in den Krieg, um ihren Gegnern «die Scheiße aus dem Leib zu prügeln«. Ist die Operation erfolgreich (oder zeigt der Gegner »Schiss« und unterwirft sich freiwillig), wird das Territorium neu abgesteckt.
Auch wenn der Prozess der Zivilisation Technologien hervorbrachte, die die Kacke von einst durch Megatonnen-Bomben ersetzten, die grundlegende Struktur ist dieselbe geblieben. »Für Saddam, in Liebe« signierte der damalige Verteidigungsminister Dick Cheney (im ersten Golfkrieg) eine über dem Irak abgeworfene Bombe. Er konnte nicht einfach »du dreckiger Scheißer« drauf schreiben, ohne seinen Job zu gefährden, sondern musste sich damit begnügen, seinem Bömbchen (frz. pétard, engl. fart, dtsch. »Furz«) eine ironische Duftmarke anzuheften: »in Liebe«. Diese Kulturleistung immerhin haben 50.000 Jahre Primatenevolution erbracht. Wäre da nicht die gesteigerte Tötungseffizienz der Mittel, man könnte fast von »Fortschritt« sprechen.
Wo geht es zu den höheren Schaltkreisen?
Mit der steigenden Zahl und Heterogenität der Bewohner gerät der Landgewinn starker Primatenbanden irgendwann an den kritischen Punkt, an dem Hierarchie und Hackordnung zu zerfasern drohen, Stabilität im Inneren lässt sich nur aufrecht erhalten über einen äußeren Feind, gegen den sich alle zusammenschließen müssen, weil er angeblich allen ans Eingemachte will. An dieser Stelle im Häufchen-Spiel humanoider Organisationsentwicklung nun schlägt die Stunde der »Nation«, des Primaten als Patrioten, der gegen eine angebliche Übermacht (die als »Barbaren«, »Hunnen«, »Achse des Bösen« etc. dämonisiert wird) seine Sicherheitszone auf das gesamte Territorium ausdehnt. \ Nicht das Bedürfnis nach Handel, Wandel und Kommunikation liegt dem Entstehen von Nationen zugrunde, sondern Paranoia. Wenn sie nur ausreichend Angst schüren, gelingt es den Primatenführern im Handumdrehen, im gesamten Stamm die Bereitschaft zu mobilisieren, für abstrakte Symbole (sprachliche Begriffe wie »Nation«, »Vaterland«, »Heimat« oder farbliche Zeichen wie Fahnen, Wimpel, Uniformen) in den Krieg zu ziehen.
Wie wenig 250 Jahre Aufklärung, Rationalismus, Moderne an der archaischen Dumpfheit dieses »Patridiotismus« bis dato ändern konnten, zeigen die jüngsten Kriege der Großmächte USA und Russland ebenso wie all die kleineren Gemetzel, die sich aufgehetzte Primatenhorden überall auf der Welt liefern. Dass die höheren Schaltkreise des Primatenhirns in ihrer kurzen Geschichte wunderbare Erfindungen hervorgebracht haben und zu großartigen Leistungen fähig sind, kann niemand bestreiten; solange aber die Saurierabteilung ihres Gehirns jederzeit den ganzen Laden übernehmen kann, solange muss sich „Homo stultus“ auf diesem Planeten der Affen wohl weiter gegenseitig die Scheiße aus dem Leib prügeln ...
Mathias Bröckers, Jahrgang 1954, ist Autor und freier Journalist. Er gehörte zur Gründergeneration der taz, war dort bis 1991 Kultur- und Wissenschaftsredakteur und veröffentlichte seit 1980 rund 600 Beiträge für verschiedene Tageszeitungen, Wochen- und Monatszeitschriften, vor allem in den Bereichen Kultur, Wissenschaft und Politik. Neben seiner weiteren Tätigkeit als Rundfunkautor veröffentlichte Mathias Bröckers zahlreiche Bücher. Besonders bekannt wurden seine internationalen Bestseller „Die Wiederentdeckung der Nutzpflanze Hanf“ (1993), „Verschwörungen, Verschwörungstheorien und die Geheimnisse des 11.9.“ (2002) und „Wir sind immer die Guten – Ansichten eines Putinverstehers“ (2016, mit Paul Schreyer) sowie "Mythos 9/11 - Die Bilanz eines Jahrhundertverbrechens" (2021). Mathias Bröckers lebt in Berlin und Zürich und bloggt auf broeckers.com.
Sein aktuelles Buch "Inspiration, Konspiration, Evolution – Gesammelte Essays und Berichte aus dem Überall" – hier im Handel
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ c3f12a9a:06c21301
2025-04-19 10:09:45
@ c3f12a9a:06c21301
2025-04-19 10:09:45Satoshi’s Time-Traveling for Knowledge #4: Liberland 2024 – Freedom Under Siege
What is Liberland?
While digging through old decentralized forums archived on the Interchain, Satoshi came across a curious name: Liberland.
“A sovereign libertarian micronation on the Danube? Founded in 2015 via Terra nullius? Built on the principles of freedom, voluntaryism, and Bitcoin? And I’ve never heard of it?”
Intrigued, Satoshi began to research. The story was almost too good to be true. A 7-square-kilometer patch of unclaimed land between Croatia and Serbia, turned into a symbol of decentralized governance and individual liberty.
No taxes unless voluntary. Bitcoin as the national currency. A digital nation-state with thousands of registered e-citizens, and even its own constitution. And yet—no recognition, no borders, and no peace.His curiosity turned into determination. He calibrated the temporal coordinates on his chrono-node to the Danube River in 2024, a year rumored to be turbulent for the Free Republic of Liberland.
When he arrived, reality struck harder than the legend.
Freedom Under Siege
The nation was under siege.
The scent of burnt wood and trampled earth lingered in the air as Satoshi stepped into what remained of the Liberland settlement. Broken structures, crushed solar panels, and a few scattered personal belongings were all that testified to the once-vibrant hub of liberty pioneers.
He found a group of residents—mud-streaked, exhausted, but defiant—gathered around the remnants of a communal kitchen. One of them, wearing a weathered Liberland t-shirt and a crypto-wallet hardware device on a chain around his neck, greeted him:
"You're not with them, are you?"
Satoshi shook his head.
"Just... passing through. What happened here?"
The man’s voice trembled between rage and sorrow:
"On the International Day of Peace, no less. Croatian police raided us. Bulldozers came with them. Took everything—generators, comms gear, even our medical tents. Claimed it was 'illegal occupation of Croatian forestry land.' But no court, no hearing. Just force."
Satoshi listened, taking mental snapshots of their faces, their words, their pain. He thought about the dream—of a place built voluntarily, where people governed themselves, free from coercion.
But that dream was burning at the edges, like the collapsed tents scattered behind them.
Reflections Under the Stars
As night fell over the Danube, Satoshi sat alone, watching the stars reflect on the black water. Thoughts spiraled:
"Decentralization... is beautiful. But without protection, it's fragile."
He realized that so long as central authorities hold monopoly on violence and taxation, every independent effort to decentralize the world—from Bitcoin to Liberland—is at risk of being suppressed, ignored, or destroyed. Not because it’s wrong, but because it's inconvenient to power.
"Unless a major state like the USA decentralizes itself from within," he thought, "true decentralization will remain a resistance—never the standard."
He activated his chrono-node once more. Not in defeat, but with purpose.
The next destination? Unknown. But the mission was clearer than ever.
originally posted at https://stacker.news/items/947954
-
 @ 2e8970de:63345c7a
2025-04-19 08:53:14
@ 2e8970de:63345c7a
2025-04-19 08:53:14originally posted at https://stacker.news/items/947930
-
 @ a296b972:e5a7a2e8
2025-04-19 12:58:33
@ a296b972:e5a7a2e8
2025-04-19 12:58:33Völkerstrafgesetzbuch (VStGB)\ § 13 Verbrechen der Aggression ==============================
(1) Wer einen Angriffskrieg führt oder eine sonstige Angriffshandlung begeht, die ihrer Art, ihrer Schwere und ihrem Umfang nach eine offenkundige Verletzung der Charta der Vereinten Nationen darstellt, wird mit lebenslanger Freiheitsstrafe bestraft.
(2) Wer einen Angriffskrieg oder eine sonstige Angriffshandlung im Sinne des Absatzes 1 plant, vorbereitet oder einleitet, wird mit lebenslanger Freiheitsstrafe oder mit Freiheitsstrafe nicht unter zehn Jahren bestraft. Die Tat nach Satz 1 ist nur dann strafbar, wenn
1.
der Angriffskrieg geführt oder die sonstige Angriffshandlung begangen worden ist oder
2.
durch sie die Gefahr eines Angriffskrieges oder einer sonstigen Angriffshandlung für die Bundesrepublik Deutschland herbeigeführt wird.
(3) Eine Angriffshandlung ist die gegen die Souveränität, die territoriale Unversehrtheit oder die politische Unabhängigkeit eines Staates gerichtete oder sonst mit der Charta der Vereinten Nationen unvereinbare Anwendung von Waffengewalt durch einen Staat.
(4) Beteiligter einer Tat nach den Absätzen 1 und 2 kann nur sein, wer tatsächlich in der Lage ist, das politische oder militärische Handeln eines Staates zu kontrollieren oder zu lenken.
(5) In minder schweren Fällen des Absatzes 2 ist die Strafe Freiheitsstrafe nicht unter fünf Jahren.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
(Bild von pixabay)
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ da0b9bc3:4e30a4a9
2025-04-19 07:22:28
@ da0b9bc3:4e30a4a9
2025-04-19 07:22:28Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/947905
-
 @ 000002de:c05780a7
2025-04-18 17:20:16
@ 000002de:c05780a7
2025-04-18 17:20:16"Focus on the things you are for, not the things you are against. Many people spend large chunks of their day thinking about what they hate. They are always telling you about something they dislike: this food, that subject, this political party, that coworker. You are more than your frustrations. Build your identity around what you love."
~ James Clear
I need to do better with this personally but its great food for thought.
originally posted at https://stacker.news/items/947407
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 9c9d2765:16f8c2c2
2025-04-19 12:11:26
@ 9c9d2765:16f8c2c2
2025-04-19 12:11:26CHAPTER SEVEN
The grand wedding hall was adorned with glittering chandeliers and pristine floral arrangements, setting the stage for an opulent celebration. The event was one of the most talked-about in the city, as it marked the union of two powerful families. Among the guests were elite businessmen, influential politicians, and members of high society, all dressed in their finest attire.
James, who had accompanied his wife Rita, found himself in an environment where he was not welcome. Though he had been invited due to his connection to the Ray family, his presence was met with disdain by many, especially by those who viewed him as an outsider.
Seated at a distant table, he remained quiet, observing the celebrations unfold. His discomfort grew when Mark, the prime minister's son and his biggest rival, walked towards him with a smug smile.
Mark had been watching James since his arrival. Seeing an opportunity to further humiliate him, he decided to strike.
“Well, well, if it isn’t the beggar who stumbled into luxury,” Mark sneered loud enough for the surrounding guests to hear. A wave of laughter rippled through the crowd. “James, I’m surprised you even found a suit for the occasion. Did you borrow it from charity?”
James clenched his fists but remained composed. He had learned long ago that reacting to Mark’s provocations only gave him more power.
As James remained silent, Mark’s expression turned cruel. He turned to the security guards stationed at the hall’s entrance and gestured towards James.
“What is this lowlife doing in such a respectable gathering? Remove him at once.”
Gasps erupted throughout the hall. Mark’s words had taken the insult to a whole new level, and now the guests watched in anticipation.
Rita, who had been engaged in conversation across the room, turned just in time to see the guards moving toward her husband. Her eyes widened in horror, and she immediately started making her way toward him.
Just as the guards reached for James, a voice echoed through the hall, freezing everyone in place.
“Stand down!”
The authoritative command came from the far end of the room, where an older gentleman had risen from his seat. The man was none other than Charles, James’s uncle, a respected business tycoon known for his influence and sharp business acumen. He had been observing the evening unfold, and now, seeing the unjust treatment of his nephew, he decided to step in.
The guards hesitated, unsure of what to do next. Charles stepped forward, his piercing gaze locked onto Mark.
“Mr. Mark, you do not have the authority to remove my family from this gathering,” Charles declared, his voice unwavering. “James is not a beggar. In fact, he is more of a man than half of the so-called gentlemen in this room.”
A tense silence followed his words. Mark’s smug demeanor faltered, his confidence wavering as he was confronted by someone of Charles’s stature.
“Uncle Charles,” James muttered in disbelief. He then quickly gave his uncle a sharp signal, a subtle but firm shake of his head. Charles understood immediately James did not want his true identity to be revealed just yet.
Charles hesitated for a brief moment before nodding slightly. He turned his attention back to the guards. “You heard me. Let him be.” “Uncle Charles,” James muttered in disbelief.
Charles turned to James and placed a firm hand on his shoulder. “You do not need to tolerate this kind of treatment, James. Come with me.”
With Charles by his side, James walked past the stunned crowd, who now murmured among themselves. Mark, visibly enraged by the intervention, clenched his jaw but said nothing. His attempt to publicly humiliate James had backfired spectacularly.
Rita caught up with them as they exited the main hall. She grasped James’s hand, her eyes filled with both relief and gratitude towards Charles.
“I’m so sorry, James,” she whispered. “I should’ve never left your side.”
James gave her a reassuring nod. “It’s not your fault, Rita. This was bound to happen sooner or later.”
Charles guided them into a private lounge where they could talk freely.
“You have tolerated enough disrespect, James,” Charles stated. “You have potential, and I believe in your abilities. Hiding your identity shouldn't make people look down on you.”
The tension in the wedding hall had shifted dramatically. Where James once stood as the object of mockery, he now commanded an air of quiet authority. The unexpected intervention by his uncle, Charles, had not only saved him from public disgrace but had also left the entire Ray family reeling in confusion.
As Mark, Edward, and Jaff stood before James, their expressions were a mixture of forced humility and barely concealed resentment. Under Charles’s orders and the mounting pressure from other influential guests, the three men reluctantly apologized.
“I… I apologize for my words earlier,” Mark muttered through clenched teeth, his pride burning with each word. “It was inappropriate.”
Edward and Jaff, though reluctant, followed suit. Their apologies lacked sincerity, but in the presence of Charles and other powerful figures, they had no choice but to comply. The entire hall watched in stunned silence.
From their reserved table, Helen, Christopher, Susan and Stephen observed the entire exchange with growing disbelief. Their carefully constructed world, where James was nothing more than an unwanted outsider, was suddenly being challenged. Even Susan, who had just returned from school, whispered to her mother, “Why is this man defending James so much?”
Helen’s eyes narrowed. “It’s sympathy. Charles has always had a soft spot for the weak.”
Christopher, however, was less convinced. “No, this is something more,” he murmured. “Men like Charles don’t go out of their way to defend someone unless there’s a reason.”
Stephen scoffed. “Whatever the reason, it won’t change anything. Mark is still the better option for Rita.”
But deep inside, they all felt uneasy. Something about James’s newfound dignity didn’t sit right with them.
Later that evening, after the wedding festivities had subsided, the Ray family gathered in the estate’s private lounge. Rita was notably absent, having left with James after the confrontation. Helen, sitting at the head of the room, was visibly irritated.
“We need to understand what’s going on,” she snapped. “Charles’s intervention was unexpected, and his protection of James was unnecessary. What could possibly warrant such treatment?”
Christopher leaned forward. “I did some digging… Charles has been looking for a driver. It’s possible he sees James as one.”
“Ridiculous,” Stephen scoffed. “James? The man we humiliated for years? There’s no way Charles would entrust his car to someone like him.”
Susan, still unsure of where she stood, hesitated before speaking. “But… what if James isn’t the same person we think he is?”
Helen slammed her hand against the table. “Enough! We will not entertain such foolish ideas. James is still a beggar compared to Mark. Mark is the prime minister’s son! That is the kind of status we need!”.
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-18 14:45:15
@ 5d4b6c8d:8a1c1ee3
2025-04-18 14:45:15We have playoff contests galore (https://stacker.news/items/947140/r/Undisciplined, https://stacker.news/items/943657/r/Undisciplined, https://stacker.news/items/945970/r/Undisciplined, https://stacker.news/items/945376/r/Undisciplined), which of course means we also have lots of playoff action to cover.
There are also several regular season contests going on (https://stacker.news/items/947153/r/Undisciplined, https://stacker.news/items/946412/r/Undisciplined, https://stacker.news/items/945561/r/Undisciplined, https://stacker.news/items/943383/r/Undisciplined), as well as the mish mash of events in the USA vs the world.
@BlokchainB posted some ideas for fixing the NBA and some of them seem promising. What really needs to be fixed?
@Coinsreporter has taken it upon himself to help us make smart decisions at Predyx. There are also some new exciting markets we want to talk about, plus just catch up on how our degeneracy is going.
The NFL Draft is this week. Stackers made their surprise picks. It's not too late to add yours to the mix. @grayruby also has some 49ers trade proposals for the Raiders number 6 pick. It'll be a tough sell.
The MLB is preposterously unbalanced. In @grayruby's words "The American League sucks".
Plus, whatever Stackers put in the comments.
Last, but not least, thank you to our listeners and supporters. As I write this, we're the #38 podcast on Fountain and Episode 27 is the #38 episode.
originally posted at https://stacker.news/items/947216
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-18 13:33:54
@ 5d4b6c8d:8a1c1ee3
2025-04-18 13:33:54This is our fastest turnaround. The 1st round of the playoffs starts tomorrow and the Play-In Tournament doesn't end until tonight.
We don't know the 8th seeds yet but all the other matchups are set. Don't forget to set your brackets for the Playoff Bracket Challenge, either.
Matchups (seed)
Clippers (5) @ Nuggets (4) Bucks (5) @ Pacers (4) Timberwolves (6) @ Lakers (3) Pistons (6) @ Knicks (3) Warriors (7) @ Rockets (2) Magic (7) @ Celtics (2) TBD (8) @ Thunder (1) TBD (8) @ Cavaliers (1)
You need to select one team from this round to win their series. You also need to predict who will be the highest scoring player in this round. You have until tip-off to select a team or player.
Scoring this round 1 Point for your team winning + Your team's seed if they win + 1 Point for picking the correct top scorer
This round has a maximum of 10 points.
Prize 10k sats (or sum of zaps on contest posts, whichever is larger)
cc: @gnilma, @BlokchainB, @grayruby, @Carresan, @fishious, @Coinsreporter, @WeAreAllSatoshi
originally posted at https://stacker.news/items/947140
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 23a2c1c3:8a8bfa1f
2025-04-19 10:25:00
@ 23a2c1c3:8a8bfa1f
2025-04-19 10:25:00Verum sine mendacio, certum et verissimum. Quod est inferius est sicut quod est superius, et quod est superius est sicut quod est inferius ad perpetranda miracola Rei Unius. Et sicut omnes res fuerunt Uno, meditatione Unius: sic omnes res natae fuerunt ab hac Una re adaptatione. Pater eius est Sol, mater eius Luna. Portavit illud ventus in ventre suo. Nutrix eius terra est. Pater omnis telesmi totius mundi est hic. Vis eius integra est, si versa fuerit in terram. Separabis terram ab igne, subtile a spisso, suaviter cum magno ingenio. Ascendit a terra in coelum, iterumque descendit in terram, et recipit vim superiorum et inferiorum. Sic habes gloriam totius mundi. Ideo fugiet a te omnis obscuritas. Hic est totius fortitudinis fortitudo fortis, quia vincet omnem rem subtilem; omnemque solidam penetrabit: Sic mundus creatus EST. Hinc erunt adaptationes mirabiles, quarum modus hic est. Itaque vocatus sum Hermes Trismegistus, habens tres partes philosophiae totius mundi. Completum est quod dixi de operatione solis.
-
 @ 7d33ba57:1b82db35
2025-04-19 10:11:08
@ 7d33ba57:1b82db35
2025-04-19 10:11:08Erfurt, the capital of Thuringia, is one of Germany’s best-kept secrets. With its fairytale old town, half-timbered houses, towering cathedrals, and cobbled streets, Erfurt offers a perfect blend of history, culture, and charm —without the tourist crowds.
🏰 Top Things to See in Erfurt
🌉 Krämerbrücke (Merchants' Bridge)
- One of Europe’s longest inhabited medieval bridges
- Lined with boutique shops, artisan studios, and quaint cafés
- A picture-perfect spot for photos and people-watching
⛪ Erfurt Cathedral & Severikirche
- Two stunning Gothic churches side by side on Domplatz (Cathedral Square)
- Climb the steps for panoramic views, especially magical during sunset or the Christmas market
🏫 Augustinerkloster (Augustinian Monastery)
- Where Martin Luther lived as a monk before launching the Reformation
- Peaceful cloisters and a fascinating exhibit on his life
🕍 Petersberg Citadel
- A baroque fortress with sweeping views of the city
- Stroll the ramparts or relax in the surrounding green spaces
🎨 Local Culture & Vibe
- Erfurt is a university town, so it feels lively, young, and creative
- Great for bookstores, independent cinemas, and music cafés
- The mix of medieval structures and modern flair gives it a unique edge
🎄 Seasonal Highlights
- 🌸 Spring/Summer: Flower-filled parks, open-air concerts, and river walks
- 🎭 DomStufen Festival (summer): Operas and plays on the cathedral steps
- 🎄 Christmas Market: One of Germany’s most beautiful, set on Domplatz beneath twinkling lights and Gothic towers
🍽️ What to Eat in Erfurt
- Try Thüringer Rostbratwurst (local sausage) from a street stand
- Don’t miss Thüringer Klöße (potato dumplings), hearty stews, and apple cake
- Cozy up with local beer or wine in one of the traditional inns
🚆 Getting There
- Just 2 hours by train from Berlin or Frankfurt
- Compact and walkable—perfect for exploring on foot or by rental bike
-
 @ 005bc4de:ef11e1a2
2025-04-19 12:23:14
@ 005bc4de:ef11e1a2
2025-04-19 12:23:14A new game is starting today, 4/19/2025, called "Moon"
https://moon.hive.pizza
I'm not a gamer and don't know much about this one, or any games for that matter, but some folks may be interested in getting in at the start.
Go-time is noon EST today, I believe.
I do get a kick out of the line "Free dopamine and tears."
😀

-
 @ 732c6a62:42003da2
2025-03-09 22:36:26
@ 732c6a62:42003da2
2025-03-09 22:36:26Não são recentes as táticas da esquerda de tentar reprimir intelectualmente seus opositores na base do deboche, da ironia, do desprezo e do boicote à credibilidade. Até Marx usava ironia para chamar os críticos de "burgueses iludidos". A diferença é que, no século XXI, trocaram o manifesto comunista por threads no Twitter e a dialética por memes de mau gosto.
A Falácia da Superioridade Moral
O debate sobre o "pobre de direita" no Brasil é contaminado por uma premissa tácita da esquerda: a ideia de que classes baixas só podem ter consciência política se aderirem a pautas progressistas. Quem ousa divergir é tratado como "traidor de classe", "manipulado", "ignorante", ou até vítimas de deboches como alguma pessoa com um qi em temperatura ambiente repetir diversas vezes "não é possível que ainda exista pobre de direita", "nunca vou entender pobre de direita", ou "pobre de direita é muito burro, rico eu até entendo", como se o autor dessas frases fosse o paladino dos mais oprimidos e pobres. Esse discurso, porém, não resiste a uma análise empírica, histórica ou sociológica.
Contexto Histórico: A Esquerda e o Mito do "Voto Consciente"
A noção de que o pobre deve votar na esquerda por "interesse de classe" é herança do marxismo ortodoxo, que via a política como mero reflexo da posição econômica. No entanto, a realidade é mais complexa:
- Dados do Latinobarómetro (2022): 41% dos brasileiros de baixa renda (até 2 salários mínimos) apoiam redução de impostos e maior liberdade econômica — pautas tradicionalmente associadas à direita.
- Pesquisa IPEC (2023): 58% dos pobres brasileiros priorizam "segurança pública" como principal demanda, acima de "distribuição de renda".
Esses números não são acidentais. Refletem uma mudança estrutural: o pobre moderno não é mais o "operário industrial" do século XX, mas um empreendedor informal, motorista de app, ou microempresário — figuras que valorizam autonomia e rejeitam paternalismo estatal. Eles dizem não entender o pobre de direita e que nunca vai entendê-los, mas o fato é que não entendem porque nunca conversaram com um sem fazer cara de psicólogo de posto de saúde. Sua "preocupação" é só uma máscara para esconder o desprezo por quem ousa pensar diferente do seu manual de "oprimido ideal".
Se ainda não entenderam:
Direita ≠ rico: Tem gente que trabalha 12h/dia e vota em liberal porque quer ser dono do próprio negócio, não pra pagar mais taxação pra você postar meme no Twitter.
Acham que são o Sherlock Holmes da pobreza: o palpite de que "o pobre é manipulado" é tão raso quanto sua compreensão de economia básica.
A Psicologia por Trás do Voto Conservador nas Periferias
A esquerda atribui o voto pobre em direita a "falta de educação" ou "manipulação midiática". Essa tese é não apenas elitista, mas cientificamente falsa:
Análise Psicológica Básica (para você que se acha o Paulo Freire):
- Síndrome do Branco Salvador: Acha que o pobre é uma criatura tão frágil que precisa de você pra pensar. Spoiler: ele não precisa.
- Viés da Superioridade Moral: "Se você é pobre e não concorda comigo, você é burro". Parabéns, recriou a escravidão intelectual.
- Efeito Dunning-Kruger: Não sabe o que é CLT, mas dá palpite sobre reforma trabalhista.- Estudo da Universidade de São Paulo (USP, 2021): Entre moradores de favelas, 63% associam políticas de segurança dura (como "bandido bom é bandido morto") à proteção de seus negócios e famílias. Para eles, a esquerda é "branda demais" com o crime.
- Pesquisa FGV (2020): 71% dos trabalhadores informais rejeitam aumentos de impostos, mesmo que para financiar programas sociais. Motivo: já sofrem com a burocracia estatal para legalizar seus negócios.
Esses dados revelam uma racionalidade prática: o pobre avalia políticas pelo impacto imediato em sua vida, não por abstrações ideológicas. Enquanto a esquerda fala em "reforma estrutural" e tenta importar discursos estrangeiros para debate, por exemplo, o tema irrelevante do pronome neutro, ele quer resolver problemas como:
- Violência (que afeta seu comércio);
- Impostos (que consomem até 40% do lucro de um camelô);
- Burocracia (que impede a legalização de sua barraca de pastel).
Religião, Valores e a Hipocrisia do "Ateísmo de Redes Sociais"
A esquerda subestima o papel da religião na formação política das classes baixas. No Brasil, 76% dos evangélicos são pobres (Datafolha, 2023), e suas igrejas promovem valores como:
- Família tradicional (contra pautas progressistas como ideologia de gênero em escolas);
- Auto-responsabilidade (ênfase em "trabalho duro" em vez de assistencialismo).Exemplo Concreto:
Nas favelas de São Paulo, pastores evangélicos são frequentemente eleitos a cargos locais com plataformas anticrime e pró-mercado. Para seus eleitores, a esquerda urbana (que defende descriminalização de drogas e críticas à polícia) representa uma ameaça ao seu estilo de vida.
A Esquerda e seu Desprezo pela Autonomia do Pobre
O cerne do debate é a incapacidade da esquerda de aceitar que o pobre possa ser autônomo. Algumas evidências:
O Caso dos Empreendedores Informais
- Segundo o IBGE (2023), 40% dos trabalhadores brasileiros estão na informalidade. Muitos veem o Estado como obstáculo, não aliado. Políticas de direita (como simplificação tributária) são mais atraentes para eles que o Bolsa Família.
A Ascensão do Conservadorismo Periférico
- Pessoas assim tem um pensamento simples. Sua mensagem: "Queremos empreender, não depender de político."
A Rejeição ao "Vitimismo"
- Pesquisa Atlas Intel (2022): 68% dos pobres brasileiros rejeitam o termo "vítima da sociedade". Preferem ser vistos como "lutadores".
A projeção freudiana "o pobre é burro porque eu sou inteligente"
O deboche esquerdista esconde um complexo de inferioridade disfarçado de superioridade moral. É a Síndrome do Salvador em sua forma mais patética:
- Passo 1: Assume-se que o pobre é um ser desprovido de agência.
- Passo 2: Qualquer desvio da narrativa é atribuído a "manipulação da elite".
- Passo 3: Quem critica o processo é chamado de "fascista".Exemplo Prático:
Quando uma empregada doméstica diz que prefere o livre mercado a programas sociais, a esquerda não pergunta "por quê?" — ela grita "lavagem cerebral!". A ironia? Essa mesma esquerda defende a autonomia feminina, exceto quando a mulher é pobre e pensa diferente.Dados Globais: O Fenômeno Não é Brasileiro
A ideia de que "pobre de direita" é uma anomalia é desmentida por evidências internacionais:
- Estados Unidos: 38% dos eleitores com renda abaixo de US$ 30k/ano votaram em Trump em 2020 (Pew Research). Motivos principais: conservadorismo social e rejeição a impostos. A esquerda: "vítimas da falsa consciência". Mais um detalhe: na última eleição de 2024, grande parte da classe "artística" milionária dos Estados Unidos, figuras conhecidas, promoveram em peso a Kamala Harris, do Partido Democrata. Percebe como a esquerda atual é a personificaçãoda burguesia e de só pensar na própria barriga?
- Argentina: Javier Milei, libertário radical, quando candidato, tinha forte apoio nas villas miseria (favelas). Seu lema — "O estado é um parasita" — ressoa entre quem sofria com inflação de 211% ao ano.
- Índia: O partido BJP (direita nacionalista) domina entre os pobres rurais, que associam a esquerda a elites urbanas desconectadas de suas necessidades.
A história que a esquerda tenta apagar: pobres de direita existem desde sempre
A esquerda age como se o "pobre de direita" fosse uma invenção recente do MBL, mas a realidade é que classes baixas conservadoras são regra, não exceção, na história mundial:
- Revolução Francesa (1789): Camponeses apoiaram a monarquia contra os jacobinos urbanos que queriam "libertá-los".
- Brasil Imperial: Escravos libertos que viraram pequenos proprietários rurais rejeitavam o abolicionismo radical — queriam integração, não utopia.Tradução:
Quando o pobre não segue o script, a esquerda inventa teorias conspiratórias.
A Hipocrisia da Esquerda Urbana e Universitária
Enquanto acusa o pobre de direita de "alienado", a esquerda brasileira é dominada por uma elite desconectada da realidade periférica:
- Perfil Socioeconômico: 82% dos filiados ao PSOL têm ensino superior completo (TSE, 2023). Apenas 6% moram em bairros periféricos.
- Prioridades Descoladas: Enquanto o pobre debate segurança e custo de vida, a esquerda pauta discussões como "linguagem não-binária em editais públicos" — tema irrelevante para quem luta contra o desemprego. Os grandes teóricos comunistas se reviram no túmulo quando veem o que a esquerda se tornou: não debatem os reais problemas do Brasil, e sim sobre suas próprias emoções.
"A esquerda brasileira trocou o operário pelo influencer progressista. O pobre virou um personagem de campanha, não um interlocutor real."
A diversidade de pensamento que a esquerda não suporta
A esquerda prega diversidade — desde que você seja diverso dentro de um checklist pré-aprovado. Pobre LGBTQ+? Herói. Pobre evangélico? Fascista. Pobre que abre MEI? "Peão do capitalismo". A realidade é que favelas e periferias são microcosmos de pluralidade ideológica, algo que assusta quem quer reduzir seres humanos a estereótipos.
Respostas aos Argumentos Esquerdistas (e Por que Falham)
"O pobre de direita é manipulado pela mídia!"
- Contradição: Se a mídia tradicional é dominada por elites (como alegam), por que grandes veículos são abertamente progressistas? A Record (evangélica) é exceção, não regra.
Contradição Central:
Como explicar que, segundo o Banco Mundial (2023), países com maior liberdade econômica (ex.: Chile, Polônia) reduziram a pobreza extrema em 60% nas últimas décadas, enquanto modelos estatizantes (ex.: Venezuela, Argentina com o governo peronista) afundaram na miséria? Simples: a esquerda prefere culpar o "neoliberalismo" a admitir que o pobre com o mínimo de consciência quer emprego, não esmola.Dado que Machuca:
- 71% das mulheres da periferia rejeitam o feminismo radical, associando-o a "prioridades distantes da realidade" (Instituto Locomotiva, 2023)."Ele vota contra os próprios interesses!"
- Falácia: Pressupõe que a esquerda define o que é o "interesse do pobre". Para um pai de família na Cidade de Deus, ter a boca de fogo fechada pode ser mais urgente que um aumento de 10% no Bolsa Família.
O pobre de direita não é uma anomalia. É o produto natural de um mundo complexo onde seres humanos têm aspirações, medos e valores diversos. Enquanto a esquerda insiste em tratá-lo como um projeto fracassado, ele está ocupado:
- Trabalhando para não depender do governo.
- Escolhendo religiões que dão sentido à sua vida.
- Rejeitando pautas identitárias que não resolvem o custo do gás de cozinha."É falta de educação política!"
- Ironia: Nos países nórdicos (modelo da esquerda), as classes baixas são as mais conservadoras. Educação não correlaciona com progressismo.
Por que o Debuste Precisa Acabar
A insistência em descredibilizar o pobre de direita revela um projeto de poder fracassado. A esquerda, ao substituir diálogo por deboche, perdeu a capacidade de representar quem mais precisaria dela. Enquanto isso, a direita — nem sempre por virtude, mas por pragmatismo — capturou o descontentamento de milhões com o status quo.
O pobre de direita existe porque ele não precisa da permissão do rico de esquerda para pensar. A incapacidade de entender isso só prova que a esquerda é a nova aristocracia.
Último Dado: Nas eleições de 2022, Tarcísio de Freitas (direita) venceu em 72% das favelas de São Paulo. O motivo? Seu discurso anti-burocracia e pró-microempreendedor.
A mensagem é clara: o pobre não é um projeto ideológico. É um agente político autônomo — e quem não entender isso continuará perdendo eleições.
A esquerda elitista não odeia o pobre de direita por ele ser "irracional". Odeia porque ele desafia o monopólio moral que ela construiu sobre a miséria alheia. Enquanto isso, o pobre segue sua vida, ignorando os berros de quem acha que sabem mais da sua vida que ele mesmo.
Pergunta Retórica (Para Incomodar):
Se a esquerda é tão sábia, por que não usa essa sabedoria para entender que pobre também cansa de ser tratado como cachorro que late no ritmo errado?
Fontes Citadas:
- Latinobarómetro (2022)
- IPEC (2023)
- USP (2021): "Segurança Pública e Percepções nas Favelas Cariocas"
- FGV (2020): "Informalidade e Tributação no Brasil"
- Datafolha (2023): "Perfil Religioso do Eleitorado Brasileiro"
- Atlas Intel (2022): "Autopercepção das Classes Baixas"
- Pew Research (2020): "Voting Patterns by Income in the U.S."
- TSE (2023): "Perfil Socioeconômico dos Filiados Partidários"
Leitura Recomendada para Esquerdistas:
- "Fome de Poder: Por que o Pobre Brasileiro Abandonou a Esquerda" (Fernando Schüller, 2023)
- "A Revolução dos Conservadores: Religião e Política nas Periferias" (Juliano Spyer, 2021)
- "Direita e Esquerda: Razões e Paixões" (Demétrio Magnoli, 2019) -
 @ 39cc53c9:27168656
2025-04-09 07:59:33
@ 39cc53c9:27168656
2025-04-09 07:59:33Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-17 21:35:47
@ 5d4b6c8d:8a1c1ee3
2025-04-17 21:35:47Congrats to @gnilma and @Carresan! Thanks to Herro and Butler both having 38 points (shoutout Heat Culture) they both secured 9 points and are tied for the lead.
Now we move on to the final Play-In Round
Matchups (seed)
- Heat (10) @ Hawks (8)
- Mavericks (10) @ Grizzlies (8)
You need to select one team from this round to win their game. You also need to predict who will be the highest scoring player in this round.
Scoring this round: 1 Point for your team winning + Your team's seed if they win + 1 Point for picking the correct top scorer
This round has a maximum of 12 points.
Prize
10k sats (or sum of zaps on contest posts, whichever is larger)
originally posted at https://stacker.news/items/946686
-
 @ 1bc70a01:24f6a411
2025-04-19 09:58:54
@ 1bc70a01:24f6a411
2025-04-19 09:58:54Untype Update
I cleaned up the AI assistant UX. Now you can open it in the editor bar, same as all other actions. This makes it a lot easier to interact with while having access to normal edit functions.
AI-generated content
Untype uses OpenRouter to connect to various models to generate just about anything. It doesn't do images for now, but I'm working on that.
Automatic Title, Summary and Tag Suggestions
Added the functionality to generate titles, summaries and tags with one click.
A Brief Preview
Here is a little story I generated in Untype, ABOUT Untype:
This story was generated in Untype
Once upon a time, in the bustling digital city of Techlandia, there lived a quirky AI named Untype. Unlike other software, Untype wasn't just your everyday article composer — it had a nose for news, quite literally. Untype was equipped with a masterful talent for sniffing out the latest trends and stories wafting through the vast digital ether.
Untype had a peculiar look about it. Sporting a gigantic nose and a pair of spectacles perched just above it, Untype roamed the virtual city, inhaling the freshest gossip and spiciest stories. Its nostr-powered sensors twitched and tickled as it encountered every new scent.
One day, while wandering around the pixelated park, Untype caught a whiff of something extraordinary — a scandalous scoop involving Techlandia's mayor, Doc Processor, who had been spotted recycling old memes as new content. The scent trail was strong, and Untype's nose twitched with excitement.
With a flick of its AI function, Untype began weaving the story into a masterpiece. Sentences flowed like fine wine, infused with humor sharper than a hacker’s focus. "Doc Processor," Untype mused to itself, "tried to buffer his way out of this one with a cache of recycled gifs!"
As Untype typed away, its digital friends, Grammarly the Grammar Gremlin and Canva the Artful Pixie, gathered around to watch the genius at work. "You truly have a knack for news-sniffing," complimented Grammarly, adjusting its tiny monocle. Canva nodded, painting whimsical illustrations to accompany the hilarious exposé.
The article soon spread through Techlandia faster than a virus with a strong wifi signal. The townsfolk roared with laughter at Untype’s clever wit, and even Doc Processor couldn't help but chuckle through his embarrassment.
From that day on, Untype was celebrated not just as a composer but as Techlandia's most revered and humorous news-sniffer. With every sniff and click of its AI functions, Untype proved that in the world of digital creations, sometimes news really was just a nose away.
-
 @ 0861144c:e68a1caf
2025-04-17 16:35:23
@ 0861144c:e68a1caf
2025-04-17 16:35:23This is a following up for the conversation started by @Scoresby with the question:
what is a sustainable model for onchain Bitcoin wallet software development?
This is an extreme opinion (even for myself) but I think is the best answer to what we're pursuing as bitcoiners.
Introduction: The Paradox of Free and Critical
The Bitcoin ecosystem thrives on open-source software. It's a world where people entrust their life savings to applications they didn’t pay a cent for. This introduces a unique paradox: we demand freedom, security, and transparency, but we don’t pay for the tools that guarantee it. Even more, we value free markets and incentives, yet expect Bitcoin wallets to exist and evolve out of altruism.
So what’s the path forward? What kind of model can ensure long-term development, security patches, feature upgrades, and alignment with Bitcoin’s protocol—without betraying its ethos?
Let’s explore the current landscape of wallet monetization and build toward a model that honors the freedom Bitcoin offers.
Wallet Monetization Models
Here’s an overview of how current Bitcoin-only (or mostly Bitcoin) onchain wallets sustain themselves based on https://stacker.news/items/944967#how-could-you-pay-for-a-bitcoin-wallet-if-you-wanted-to:
| Model | Description | Example Projects | Pros | Cons | |---------------------------|-----------------------------------------------------------------------------|-------------------------------|----------------------------------------------------|------------------------------------------------------------| | Donations/Grants | Funded by community or institutional support | Bitcoin Core, Sparrow, Specter| User-focused, preserves freedom | Unstable, depends on goodwill or VC altruism | | Freemium/Subscription| Free basic app, premium features unlocked through subscriptions | Nunchuk, Keeper, Theya | Predictable revenue | Introduces centralization, relies on dev infrastructure | | Device Sales | Wallet tied to hardware devices | Bitkey, Envoy | Scalable, aligned with sovereignty | Limits access based on geography or price | | Custodial Services | Funds held by a third party | Casa, River, Swan | Simple onboarding for new users | Compromises on "Not your keys, not your coins" | | Tx Commissions| Wallet takes a fee from trades within the app | BlueWallet (speculatively, maybe not) | Transparent funding method | User becomes product; hard to avoid surveillance and KYC | | L2 Services | Monetization through Lightning routing fees or service layers | Phoenix, Breez, Zeus | Innovative, supports network growth | Not suitable for cold storage or large holdings | | Sell the Software | Direct payment for downloading or unlocking the app | (Rare or nonexistent) | Clear transaction, sustainable if valued | Cultural resistance; rare in open-source culture |
Each of these models carries tradeoffs—especially when you consider global context.
Why Context Matters: Global Finance Is Not Equal
In countries with stable banking systems (U.S., Europe, Japan), Bitcoin wallets are largely seen as savings vaults. People use their banks for spending and turn to Bitcoin as a hedge or long-term store of value. In these places, users are more comfortable with subscription models or regulated custodial solutions.
But in the global south—Latin America, North Africa, parts of Asia—Bitcoin plays a different role. Banks are distrusted, inflation is high, and people are not just saving in Bitcoin; they’re trying living on Bitcoin. Wallets aren't just tools, they’re lifelines. Asking users to subscribe, give up sovereignty, or rely on opaque intermediaries is antithetical to the entire point. Can't use bitcoin? Go straight to cash or side-banks solutions like EMP (Giros Tigo, M-PESA). Taxes? We don't care, I don't mind not pay taxes when I buy nor I care even less how to present my fill form to authorities. Bitcoin is need.
In this context, the question isn't “can I pay for a wallet?”—it's “can I use it without being surveilled, blocked, or priced out?”. That's why technologies Lightning-L2 related have some much adoption, because we need not only to save but to pay our things. Just look El Salvador, Argentina or lately Bolivia, countries that need alternative to keep receiving/sending while having a volatility index very high.
The Bitcoin Standard: Build Your Own Wallet
Under the Bitcoin standard, the sustainable model must allow any individual to create their own wallet—no permission required, no gatekeepers, no payment walls. Think of it like designing your own leather wallet to carry cash. Anyone can do it, because the knowledge is public, the materials are available, and there’s no centralized authority controlling the process.
The same is true with Bitcoin:
- Wallets can integrate privacy-enhancing tools like Whirlpool (CoinJoin).
- They can adopt PayNym or BIP47 for stealth addresses.
- Features like automated DCA (Dollar Cost Averaging) can be designed to optimize both strategy and privacy.
- Visuals can display only sats, not fiat denominations, reinforcing the mindset that Bitcoin is the native unit.
What sustains these features? A community of developers building modular, composable, interoperable tools. The protocol enables this—Bitcoin is both a financial layer and a developer’s playground.
The Custodial Dilemma: Easier, But Risky
Let’s be honest: custodial wallets make onboarding smoother. They're easier to explain. “Download app, get coins.” That’s it. But this simplicity comes at a cost.
- “Not your keys, not your coins” is not just a mantra—it’s survival.
- Custodial wallets are subject to seizure, surveillance, and censorship.
- They build bad habits: users don’t learn how to verify, back up, or transact privately.
And yet, we’ve seen it again and again: many newcomers start with custodial solutions and only move to self-custody after something goes wrong—a blocked account, a missing withdrawal, or an unexplained freeze. Then they meet the 12 words. And yes, the seed phrase is scary at first. But over time, it becomes the ultimate expression of financial freedom.
Transaction Fees: A Ticking Time Bomb
Some wallet developers seek sustainability by taking a small cut of in-app transactions. It's easy to justify: "We only take 0.5% for maintenance." But this model is fundamentally flawed in the context of Bitcoin.
- It reintroduces third-party dependence into a tool meant to eliminate it.
- It discourages self-custody by tying wallet use to an ongoing cost.
- It creates perverse incentives: developers are now driven to optimize for volume, not user sovereignty.
In the short term, this might work. But long term, it turns wallets into surveillance engines and behavioral data extractors—exactly what Bitcoin was meant to disrupt.
A sustainable model can’t be built on transaction tax. That’s fiat logic.
Conclusion: DIY Is the Only Model That Scales with Sovereignty
In Bitcoin, every decision is a reflection of trust. Who do you rely on for custody, code, and convenience? A sustainable model for wallet software must allow people to opt out at every layer. If you don’t like the wallet UI—change it. If the devs abandon the project—fork it. If the company goes under—run your own build. This is only possible because the information is free, the protocol is neutral, and the design is decentralized by nature. We don’t need more paywalls. We need more builders. More tinkerers. More people realizing that “wallet software” is not a product you buy—it’s a freedom you exercise.
That’s the Bitcoin way.
That’s the model that lasts. That's my two sats.originally posted at https://stacker.news/items/946326
-
 @ 52524fbb:ae4025dc
2025-04-09 03:36:09
@ 52524fbb:ae4025dc
2025-04-09 03:36:09 To most of us it's all about the sound of freedom, the innovation, it's technical implication, what if feels like in a decentralised environment. Now let's head into that which brings our fantasies to reality, Nostr which stands for "Notes and other stuffs Transmitted by Relays", is an open protocol designed for decentralised social networkin
To most of us it's all about the sound of freedom, the innovation, it's technical implication, what if feels like in a decentralised environment. Now let's head into that which brings our fantasies to reality, Nostr which stands for "Notes and other stuffs Transmitted by Relays", is an open protocol designed for decentralised social networkinNostr most Amazing Features
-
Decentralisation: compared to traditional social media platforms like like Twitter (X) and Instagram that rely on centralised servers, Nostr operates through a network of relays. These relays serves as servers that store and forward messages. This amazing feature of decentralisation aims to make the network completely resistant to censorship, most people would say how? To answer your question it's because no single individual control's it
-
User Control: ever thought of the purest feeling of freedom, well Nostr just gave you the space to experience. User's have total control over their data and identity.
-
Simplicity: why get stressed when Nostr got you covered? This protocol is designed to be relatively simple, making it easier for developers to build applications on top of it.

Nostr Relation to Bitcoin
Who wouldn't want to be part of a community that embraces it's ethics in a dignified manner. Nostr has gained popularity within the Bitcoin community, and the Bitcoin Lightning Network is used for features like "Zaps" (which represents small payments or tips). There are also similarities in the philosophy of decentralization, that both bitcoin and Nostr share. Just like the saying goes, birds of the same feather flock together. This leads me to one of the best magnificent project, focused on building decentralisation media infrastructure, particularly within the Nostr ecosystem.

Yakihonne the future of the world
YakiHonne is an amazing project focused on building decentralized media infrastructure, particularly within the Nostr ecosystem. It's mind blowing features includes:
-
Decentralized Media: YakiHonne aims to provide tools and platforms that support freedom and automation in content creation, curation, article writing and reporting. It leverages the decentralized nature of the Nostr protocol to achieve this amazing feat.
-
Nostr and Bitcoin Integration: YakiHonne is closely tied to the Nostr network, and it also incorporates Bitcoin functionality. This integration includes features related to the Lightning Network, enabling things like "zaps" (small Bitcoin payments) within the platform.
-
Mobile Application: YakiHonne offers a mobile application with an eye catching user interface simply designed to provide users with a smooth and intuitive Nostr experience. This app includes features like: -Support for various login options. -Content curation tools. -Lightning Network integration. -Long form article support.

Disadvantages of Traditional social media
Lets go back to a world without the flute of freedom echoing in our hearts, where implementations are controlled by certain entities, reasons why traditional social media platforms hold not even a single stance compared to Nostr:
- Privacy Concerns:
Data Collection: Social media platforms collect vast amounts of user data, often without full transparency. This data can be used for targeted advertising, and sometimes, it can be compromised in data breaches. Which won't happen or be possible on yakihonne
-
Social Comparison and Low Self-Esteem: The over hyped and often unrealistic portrayals of life on social media can lead to feelings of inadequacy and low self-esteem. But on yakihonne you get to connect and grow with a community with specified goals bent on implementation
-
Misinformation and Fake News:
Spread of False Information: Social media platforms can be breeding grounds for misinformation and fake news, which can spread rapidly and have significant real-world consequences. Is that possible on yakihonne, well we all know the answer. 4. Centralized Control:
Censorship: Centralized platforms have the power to censor content, raising concerns about freedom of speech. Algorithm Bias: Algorithms can be biased, leading to unfair or discriminatory outcomes. This tells us why a decentralised media platform like yakihonne stands out to be the only media with a future.

Why Chose Nostr why chose yakihonne
When considering Nostr and related projects like YakiHonne, the appeal stems largely from a desire for greater control, privacy, and freedom in online communication. Which from the points aligned above, gives us no second chance of thought, but the thought of being part of the Nostr community, active on a platform like yakihonne.
-
-
 @ c066aac5:6a41a034
2025-04-17 00:05:49
@ c066aac5:6a41a034
2025-04-17 00:05:49I am all about fleshing out a fantasy, even if the chances of it coming to reality are fairly slim. Dreams should be written down, meditated on, processed over long periods of time. I don't think of it as manifesting (nor do I condone manifestation); one could argue such practices are Biblical (Habakkuk 2:2).
So I'm going to write this out and make it plain, on the off chance that putting it out there brings somethings to fruition:
Jack Dorsey should take over Mozilla.
Either via an invitation from Mozilla, or via a hostile takeover. I don't really care how it happens, but I believe it should happen and I'll outline why.
The Fallen Hero

Mozilla has been having a bad time. I'm not sure that the organization has done much good since the unceremonious departure of Brenden Eich (there's Rust, but is that really a good thing?).
Firefox is losing its relevance. The FireFox Terms of Service update has sparked outrage, the removal of the promise to never sell your data was a Judas level of betrayal, FireFox currently (at the time this article was penned) makes up less than 3% of the total browser marketshare, their main source of income from Google is in jeopardy, most websites are only optimized for Chromium-based browsers, and the Gecko engine is not very secure.
Mozilla's best product is dying, and what is the organization doing about it? They're working on a plethora of issues their core user base does not care about. They've jumped on the AI hype train, they've bought an advertising company (which is very irrelevant to their user base, especially considering uBlock Orgin exists), they're selling white labeled VPNs (Mullvad), they're selling data removal services (which is powered by a former data broker), they're pushing shopping products, they're forcing features on their users which were never asked for (POCKET!!), it seems that Mozilla is completely out of touch with the people they claim to serve. They've abandoned their first love.
Thunderbird is showing some promise with the recent announcement of Thundermail, but that project will sadly suffer from guilt by association.
We have to remember though: Mozilla used to mean something in the FOSS/Open Source world.

They were the shining city on the hill of the internet. They rose up from the ashes of Netscape. FireFox kicked Internet Explorer's butt; it was a punk rock movement. Thunderbird is still an amazing email client. Rust (despite the arguing programmers) is a significant innovation in the programming language space.
I'm not rooting for the downfall of Mozilla. Sure, in a way I'd be happy about it: I'd like to see poor leadership get what it deserves, but I fear Mozilla as a symbol of FOSS/OS would send a sad signal across the ecosystem. I'm a capitalist at heart so I don't favor bailouts (nor am I calling for one); I truly believe this organization could be turned around with the right leadership. Maybe it could be as simple as going back to their original model of serving the deep pockets of the corporate world with open source tech rather than going for the wallets of the consumer.
Every problem is a leadership problem. Fix the leadership, fix the problems.
The Last Great Open Source Hero?
Sadly FOSS figures tend to die of public crucifixion. As time goes on, we have less and less great figures to point to. Thankfully, Jack hasn't been canceled yet.
Jack Dorsey has a pretty good résumé in the open source world. He jumped right in with Bitcoin. He left BlueSky for NOSTR. He would've made Twitter a protocol if he didn't need to feed himself early in his career. He is currently financing several projects in the Bitcoin and NOSTR world, which is arguably the best open source technology in the world right now.
I do believe that people should stay in their lane of expertise, and maybe Jack should. However, my message to Jack would be that it would be a shame if his passion for open source remained solely in Bitcoin and NOSTR. If his leadership was injected into the Mozilla machine, it could be steered into a magical direction.
Imagine FireFox being the first browser with layer 2 wallet integration (stick it to Brave and their BAT crap [we still love you Brenden Eich flaws and all]). Imagine having a whole world of existing talented developers suddenly interested in contributing their talents to the NOSTR community. Imagine having a browser with an engine that can actually go toe-to-toe with Chromium. Imagine an organization that once again gives FOSS a good name rather than actively eroding public confidence in FOSS.
The True FOSS Heroes

Jack is probably not going to touch Mozilla with a 150 foot pole (or see this article). We all probably need to let the Mozilla dream die in front of us.
Things aren't always black and white. I don't think of Mozilla as an evil organization; just an organization subject to the flaws of fellow humans like you and me. Even the Eye of Sauron, Google, has been a huge blessing to the open source world (Go programming language, Android, all of their open source sponsorships, many more things I could mention).
The beautiful thing about FOSS/OS is that it is a movement of the people. Titans will rise up and fall, but you and I make up the backbone of FOSS. I've had nothing but good interactions with FOSS fanatics. NOSTR's own OceanSlim taught me about Ungoogled Chromium, the Go programming language, and NOSTR relays. When I wanted to get into Linux, I was able to plug in immediately with a group of Linux users here in Nashville. NOSTR devs for the most part are happy to answer my inquiries when I slide into their DMs. I've been in group chats with people openly discussing the best way to make a great lightning wallet.
There's a lot of connection in the Open Source world that I cherish; it's very different from the corporate world most of us are immersed in. The corporate world has gatekeepers; Open Source has collaborators. The corporate world operates in the shadows to maximize profits; Open Source steps into the light for everyone's benefit. The corporate world says you'll never have enough experience/qualifications; Open Source encourages and equips you.
My point is, don't worship any organization. Be thankful for the people around you, try out FOSS programs whenever you can, and have fun with it.
All that said, I wouldn't mind if Jack took over Mozilla. Or if one of his friends took a position (ODELL?). Heck, throw Snowden in while we're at it.
Footnote: "Open Source" and "FOSS/Free and Open Source Software" are used interchangably in this article. Mistakes were made I'm sure, but I hope I got the point across.
-
 @ 2b24a1fa:17750f64
2025-04-04 08:10:53
@ 2b24a1fa:17750f64
2025-04-04 08:10:53Wir leben in einer Demokratie. So heißt es immer. Immerhin hat die Bevölkerung, der Souverän ein Mitspracherecht. Einmal alle vier Jahre. Und damit fünfundzwanzig Mal in einem Jahrhundert. Diese 25 Wahltage ergeben zeitlich 0,07 Prozent des gesamten Jahrhunderts. Würde man das Jahrhundert auf einen Tag runter rechnen, dann ergäben diese 0,07 Prozent ziemlich genau eine Minute des Mitspracherechts. Eine Minute pro Tag darf der Souverän also bestimmen, wer am restlichen Tag ungehindert schalten und walten darf – bis in das Grundgesetz hinein.
https://soundcloud.com/radiomuenchen/das-grundgesetz-als-schmierzettel-von-henry-matthes?
Die Veränderung in diesem zentralen Gesetzestexten ist allein den Parteien vorbehalten. An sämtliche Änderungen halten, dürfen sich dann nachher alle – selbst dann, wenn noch so wenige Bürger dahinterstehen.
In den letzten Wochen offenbarte sich dieser Missstand in präzedenzloser Weise. Die als Sondervermögen schön-deklarierte Neuverschuldung wurde im Grundgesetz festgeschrieben. Ist eine solch selektive Umgestaltungsmöglichkeit des wichtigsten Gesetzestext einer Demokratie würdig? Bräuchte es nicht zumindest einer Absegnung durch Volksabstimmungen?
Henry Mattheß hat sich hierzu Gedanken gemacht. Hören Sie seinen Text „Das Grundgesetz als Schmierzettel“, der zunächst auf dem Blog von Norbert Häring erschienen war.
Sprecher: Karsten Tryoke
Bild: Radio München
www.radiomuenchen.net/\ @radiomuenchen\ www.facebook.com/radiomuenchen\ www.instagram.com/radio_muenchen/\ twitter.com/RadioMuenchen
Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
-
 @ 7d33ba57:1b82db35
2025-04-19 09:20:50
@ 7d33ba57:1b82db35
2025-04-19 09:20:50Landshut, located in Lower Bavaria, is one of Germany’s most beautiful and historically rich towns. Nestled on the banks of the Isar River, it charms with colorful Gothic buildings, a majestic hilltop castle, and a walkable old town full of character. It’s less touristy than Munich, but just as captivating.
🏰 Top Things to See in Landshut
👑 Trausnitz Castle
- Built in the 13th century and perched above the town
- Offers panoramic views over the red rooftops of Landshut
- Explore medieval halls, Renaissance arcades, and quirky art collections
⛪ St. Martin's Church
- Home to the tallest brick tower in the world (130m!)
- A soaring example of Gothic architecture—stunning inside and out
🏘️ Old Town (Altstadt)
- Lined with pastel-colored townhouses and bustling cafés
- Walk the Altstadt street, full of shops, bakeries, and history
- Don’t miss Ländtor, the medieval city gate that once guarded the town
🎭 Landshuter Hochzeit (Wedding Festival)
- Every four years, Landshut hosts one of Europe’s biggest historical reenactments
- Locals dress in 15th-century costumes to recreate the wedding of Duke George and Princess Hedwig (1475)
- Expect jousting, feasting, parades, and pageantry—pure medieval magic!
🍺 What to Eat & Drink
- Try Bavarian specialties like Weißwurst, pretzels, and Schweinshaxe (pork knuckle)
- Wash it down with a cold beer from one of the local breweries—Landshuter Brauhaus is a classic
- Grab a coffee at a riverside café or enjoy cake at a traditional Konditorei
🚆 How to Get There
- Just 1 hour by train from Munich
- Easily explored on foot or by bike
- A great day trip or stopover on your way to/from southern Bavaria or Austria
🌼 Best Time to Visit
- Spring and summer for festivals, riverside walks, and sunny beer gardens
- December for cozy Christmas markets and fairy-lit old town streets
- Any time of year for history lovers and slow travel fans
-
 @ 000002de:c05780a7
2025-04-16 20:48:48
@ 000002de:c05780a7
2025-04-16 20:48:48Not only can I be my own bank and run a my own lightning bank. I can have private communications with people anywhere on the planet that only the two of us can read. On top of that I can manufacturer items in my office with this very affordable 3d printer.
Just a thought as I'm printing some items for a party we have coming up. I'm watching the print complete from my phone while I work on the back porch.
We live in an amazing time. It is easy to forget this when we are focused on the stupidity we see online.
originally posted at https://stacker.news/items/945569
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 000002de:c05780a7
2025-04-16 17:47:30
@ 000002de:c05780a7
2025-04-16 17:47:30She was a special cat. She was a tiny kitten crossing a country road far from any houses. We thought she was a rat at first. We stopped the car and I tried to find her. She was in a thicket hissing at me. She was always full of spunk. I didn't want another cat. I said we'd find her a home. But she quickly burrowed her way into my heart.
She was very vocal and affectionate. She was playful and loved to sneak up on you. She was just to curious and adventurous for her own good. We knew she'd get herself into trouble eventually but never dreamed it would be so soon.
When you open your heart, you are opening yourself up to being loved but also pain. Its bittersweet but worth it. Rest in peace Lucy. I miss that little girl.
originally posted at https://stacker.news/items/945348
-
 @ 7c05c4f6:50d03508
2025-04-19 08:33:54
@ 7c05c4f6:50d03508
2025-04-19 08:33:54 About Cooker.club
About Cooker.clubCooker.club is a decentralized AI agent platform that combines AI, music, Web3, virtual idols, and social media, allowing AI-powered creators to operate autonomously and connect with fans through Create-to-Earn. 1. What is Create-to-Earn (C2E)? Create-to-Earn (C2E) is a decentralized incentive mechanism launched by Cooker.Club to reward both AI Agent developers and token holders. By participating in the ecosystem — either by developing AI Agents or holding their tokens — users can earn $COOK tokens automatically via smart contract-based mining. 2. How much $COOK is allocated to C2E? Cooker.Club allocates 60% of the total 1,000,000,000 $COOK supply to community incentives. C2E Season 1 will distribute 200,000,000 $COOK (20% of total supply) through on-chain mining. 3. How does C2E mining work? Each supported blockchain has fixed $COOK output per block: Base: 50 $COOK per block (≈ 2 seconds/block)
BNB Chain: 75 $COOK per block (≈ 3 seconds/block)
Solana: 10 $COOK per block (≈ 0.4 seconds/block) Each block's $COOK reward is split as follows: 10% to the DEV address of each AI Agent token
90% distributed among token holders based on their share of the total market cap 4. What is a market cap multiplier? Cooker.Club assigns some AI Agent tokens a reward multiplier to boost their effective market cap for mining calculation: Multiplier values: 1x, 1.2x, or 2x
Higher multipliers lead to more $COOK rewards
This mechanism encourages early support of high-potential or platform-supported AI Agents. 5. What are early bird rewards? Early users benefit from a 4x reward multiplier during the initial mining phase: Solana: first 1,500,000 blocks
Base: first 300,000 blocks
BNB Chain: first 200,000 blocks
- Can migrated AI Agents receive bonuses? Yes. AI Agents migrated from the Virtuals platform get a 1.2x multiplier on market cap when calculating $COOK distribution. This bonus applies to both developers and token holders.
- How is $COOK distributed between AI Agent tokens? Example on Solana: 10 $COOK is produced in one block
3 tokens: A (1M cap × 2x), B (2M × 1x), C (1M × 1x) = Total adjusted cap: 5M
Token A: 4 $COOK → 0.4 to DEV, 3.6 to Holders
Token B: 4 $COOK → 0.4 to DEV, 3.6 to Holders
Token C: 2 $COOK → 0.2 to DEV, 1.8 to Holders 8. How can users earn through C2E? There are three main ways: Hold AI Agent tokens — Earn a share of $COOK rewards proportionate to the token’s market cap
Create an AI Agent — Devs receive 10% of rewards tied to their Agent’s token
Migrate a Virtuals token — Gain a 1.2x market cap multiplier To activate earning, users must complete at least one transaction on Cooker.Club. 9. What is planned for C2E Season 2 and Season 3? Each future season will also allocate 200,000,000 $COOK. 10. Why is C2E important for the Web3 AI economy? C2E introduces a sustainable, decentralized, and automated incentive loop. It empowers AI Agents to become economically autonomous and rewards supporters based on their alignment. It transforms community belief into protocol-level value, setting the foundation for an on-chain AI-native creator economy. 11. Where can I start? There are three ways to participate in C2E, depending on your role and goals: Option 1: Hold an AI Agent token (for holders) Visit https://cooker.club
Browse available AI Agents and choose one that fits your interest
Buy the Agent’s token directly
Make at least one transaction (buy/sell/transfer) to activate eligibility
Hold the token — $COOK rewards will begin distributing automatically Option 2: Create your own AI Agent (for devs) Go to https://cooker.club
Launch your AI Agent and issue a native token
Become dev & holder
Promote your Agent — the higher the token’s market cap, the more $COOK you and your holders will earn Option 3: Migrate from Virtuals (for existing AI projects) If you have an AI Agent deployed on the Virtuals platform, initiate the migration on Cooker.club
After migration, your token and all holders will receive a 1.2x market cap multiplier for C2E reward calculation
The DEV address and holders will automatically enter the reward pool
No staking. No lockups. No claiming. Just plug in — and the protocol does the rest. Visit https://cooker.club, choose an AI Agent, buy its token, and complete one transaction to activate C2E mining. No staking. No lockups. No claims. Just hold, and the protocol takes care of the rest.
For real-time updates, follow: 🌐 https://cooker.club 🌐https://medium.com/@cookerailabs
-
 @ ba36d0f7:cd802cba
2025-04-16 16:45:07
@ ba36d0f7:cd802cba
2025-04-16 16:45:071. The creative (but fleeting) pleasure of tactics
Chess tactics are like candy between meals - instant delight, but not true nourishment. Choosing whether to attack a bishop or a knight feels like picking between vanilla and chocolate ice cream: sprinkles or none, cherry on top or not...
-
They’re freedom within boundaries: the board has limits, but imagination doesn’t.
-
They mirror your style: quick strikes like an espresso? Or slow grinds like green tea?
2. Two tactics, two joys
-
Simple (an exposed king): everyday wins (like finding cash in your pocket).
-
Complex (3+ move combos): earned triumphs (like a project you’ve sweat over).
3. The Buddha’s warning: "Don’t Confuse the Sugar Rush for the Meal"
Buddhism teaches that clinging to pleasure (kāma-tanha) breeds suffering. In chess and life:
-
Tactics are desserts: sweet, but not the feast.
- Example: Beating a blunder is like winning the lottery; outplaying strategically is like building wealth.
-
The balance: Revel in that dazzling queen sacrifice - but don’t bet your game on it. Like savoring cake, not devouring the whole bakery.
4. How to play (and Live) this wisdom
✅ Ask yourself:
-
Is this move sound - or just seductive? (Like craving junk food vs. needing sustenance).
-
Am I here to win, or to wow? (Ego checkmates you faster than any opponent).
Final Move: The middle path on 64 squares
Buddhism invites joy without attachment. On the board:
-
Tactics = spice: they dazzle, but strategy feeds growth.
-
Strategy = the harvest: the patience that crowns kings.
♟️ So - do you chase the fireworks, or cultivate the long game?
Online Resources
Chess tactics - chess.com https://www.chess.com/terms/chess-tactics
Tactic examples - chess.com https://www.chess.com/article/view/chess-tactics
Tactics - lichess.org https://lichess.org/study/topic/Tactics/hot
somachess #buddhism #philosophy #chessphilosophy #chess #elsalvador #btc #apaneca #chesselsalvador
-
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ f5369849:f34119a0
2025-04-19 05:54:30
@ f5369849:f34119a0
2025-04-19 05:54:30Hackathon Summary
The BUIDL BATTLE | The Bitcoin Builders Tournament concluded with 81 projects approved from 219 registered developers. This three-week virtual event aimed to foster innovation on Bitcoin by offering significant exposure to builders, investors, and accelerators. It centered on themes such as Bitcoin DeFi and Real World Utility, with participants competing for over $90,000 in total prizes, including cash, AWS credits, and ICP grants. Notable innovations emerged, utilizing components like Stacks technology and sBTC.
The hackathon featured a two-round structure. Finalists presented their work to a panel of judges, including venture capitalists and industry leaders, to determine the overall champion. Participants received valuable insights through workshops and mentoring, with the second round boosting visibility and potential funding opportunities. Supported by partners such as Stacks Foundation and AWS, the event celebrated new talent and contributed to strengthening the Bitcoin development ecosystem.
Hackathon Winners
Bitcoin DeFi 2.0 Prize Winners
Bitcoin DeFi 2.0 focuses on improving scalability, security, and user experience. Winners in this category presented notable technical advancements and innovative solutions to address these challenges.
- BigMarket: A decentralized, AI-enabled prediction market platform on Bitcoin's Layer 2 network, Stacks. Operated by a DAO, it facilitates reliable, decentralized predictions.
- BitForward: A decentralized platform for creating NFT-backed forward contracts on Bitcoin using the Stacks blockchain.
The 3.0 Digital Economy Prize Winners
This category examines the evolution of the internet by merging finance, entertainment, and social interactions to form user-driven ecosystems in MemeFi, SocialFi, and GameFi.
- Kulture.Fun: A decentralized SocialFi chat platform with token-gated access and Bitcoin-backed features to enhance crypto community interactions.
- Skullcoin: Introduces gamification in Bitcoin DeFi by integrating sBTC, promoting interactive in-game experiences and activating BTC liquidity.
Real World Ordinals & NFT Usage Prize Winners
Focusing on practical applications beyond traditional art and memes, this category encourages exploring NFTs' potential in diverse areas.
- Offers & Counter-offers | BNS One: A marketplace enabling blockchain-based BNS name trading through smart contracts for trustless transactions.
- Truth-Chain: Utilizes blockchain technology to verify digital content authenticity and origin via the Stacks platform.
Tooling & Infrastructure Prize Winners
Innovations in this section provide frameworks and protocols essential for decentralized application development, focusing on Web3 tools.
- BLAZE PROTOCOL: Enhances the Web3 experience through Layer 2 architecture, offering instant transaction confirmations and seamless user interaction.
- PoXAgents: Uses AI agents to simplify interactions with the Stacks Blockchain for non-technical users.
ICP Challenge Prize Winners
Projects in this category integrate Internet Computer advancements to address common blockchain challenges within the Bitcoin ecosystem.
- ckBoost: Accelerates Bitcoin transactions on Internet Computer, reducing confirmation times through liquidity pools.
- CounterpartyICP: Facilitates smart contract and digital asset management on Bitcoin through a module that interfaces with the Counterparty API.
AWS - Buidl with Bedrock Challenge Prize Winner
Focusing on projects leveraging AWS technology, this category showcases innovations built on robust infrastructures.
- Stacks AI: An AI tool for generating, debugging, and learning smart contracts in Clarity, employing AWS Bedrock for scalable analysis.
For further details on all projects and innovations, visit Dorahacks.
Organization
About the organizer: Stacks Foundation
The Stacks Foundation is dedicated to advancing the growth and development of the Stacks blockchain - the leading Bitcoin layer 2. It supports a variety of projects that leverage Bitcoin's security to empower a decentralized internet. Through initiatives like the Stacks Accelerator, the Foundation has significantly contributed to the blockchain ecosystem by fostering innovation and developer engagement. Its current mission is focused on enhancing tools and resources for developers to build user-owned applications, reinforcing its commitment to the decentralized web.
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ ba36d0f7:cd802cba
2025-04-16 16:39:58
@ ba36d0f7:cd802cba
2025-04-16 16:39:581. El placer creativo (pero efímero) de las tácticas
Las tácticas en ajedrez son como las golosinas entre comidas: satisfacción inmediata, pero no sustento real. Escoger entre atacar a un alfil o un caballo puede ser como elegir entre helado de vainilla o chocolate - con chispas o sin chispas, cereza o sin cereza....
-
Son libertad dentro de las reglas: el tablero es finito, pero la creatividad no.
-
Reflejan tu estilo: ¿ataques rápidos como un espresso? ¿O finales lentos como un té verde?
2. Dos tipos de tácticas, dos tipos de placeres
-
Sencillas (como un rey descubierto): placeres cotidianos (como un golpe de buena suerte).
-
Complejas (combinaciones de 3+ jugadas): placeres que exigen planificación (como cumplir metas).
3. La advertencia budista: "No confundas el postre con la cena"
El Buddha enseñó que aferrarse a los placeres (kāma-tanha) genera sufrimiento. En ajedrez y en la vida:
-
Las tácticas son golosinas: te dan ventaja, pero no son estrategia.
- Ejemplo: Ganar por un descuido del rival es como heredar dinero; ganar por planificación es como construir un negocio.
-
El equilibrio: Disfruta ese sacrificio de dama espectacular… pero no bases tu juego en ellos. Como saborear un pastel ocasional sin volverse adicto al azúcar.
4. Cómo aplicar esto en el tablero (y en la vida)
✅ Pregúntate siempre:
-
¿Esta táctica es sólida o solo emocionante? (Como diferenciar antojo de hambre real).
-
¿Estoy jugando para ganar… o para impresionar? (El ego es peor enemigo que el rival).
Conclusión: El camino medio (ajedrecístico)
El budismo no pide renunciar a los placeres, sino disfrutarlos sin apego. En el ajedrez:
-
Tácticas = especias: dan sabor, pero no son el plato principal.
-
Estrategia = nutrición: lo que realmente te hace mejor jugador.
♟️ ¿Y tú? ¿Eres de los que prefieren un ataque brillante (aunque riesgoso) o una victoria lenta pero segura?
Recursos en linea
Tácticas - chess.com https://www.chess.com/es/article/view/tacticas-ajedrez
Problemas de ajedrez - chess.com https://www.chess.com/es/puzzles
Tácticas - lichess.org https://lichess.org/study/qgLXlnIF/udsuAudN
ajedrez #somachess #chess #chesselsalvador #budismo #budhism #filosofia #philosophy #apaneca #rutadelasflores #article #longform #articulo
-
-
 @ ba36d0f7:cd802cba
2025-04-16 15:09:25
@ ba36d0f7:cd802cba
2025-04-16 15:09:25What is Checkmate?
Checkmate is the decisive move that ends the game. It occurs when the king is under direct threat (in check) and there’s no legal move to save it: neither capturing the attacking piece, blocking the attack, nor fleeing to a safe square.
Unlike other pieces, the king can never be captured - its downfall marks the end of the game. Thus, when escape is impossible, the game ends immediately. There’s no need to "take" the king; its fate is already sealed.
How to Achieve Checkmate?
It requires:
-
Imminent Threat: One or more pieces attacking the enemy king.

-
Total Blockade: All escape squares controlled by the opponent.

- No Possible Defense: No piece can intercept the attack.

Basic Example: The Back-Rank Mate (with a rook or queen on the last rank, where the king can’t escape due to being blocked by its own pieces).
1. The First Chess Commandment: Seek Checkmate
In every game, each move should begin with an essential question: Is there a checkmate in this position? - for both yourself and your opponent. If not, the game revolves around material advantage or positional control. But this order isn’t arbitrary:
-
A tactical oversight can ruin a dominant position.
-
A missed checkmate means instant defeat.
Classic Example: The Scholar’s Mate (1.e4 e5 2.Bc4 Nc6 3.Qh5 Nf6?? 4.Qxf7#).
 White wins because Black, focused solely on development, ignored the deadly threat.
White wins because Black, focused solely on development, ignored the deadly threat.➡ Reflection: In strategy, as in life, the urgent (survival) precedes the important (victory).
2. The Philosophy of the Board: When Advantages Aren’t Enough
A lone king can evade capture forever if the opponent doesn’t know how to checkmate. Similarly, in human existence, advantages - talent, resources, or opportunities - are worthless if not transformed into decisive actions.
-
What good is controlling the center if you can’t convert it into an attack?
-
What good are privileges if not used to build something meaningful?
Chess, like life, rewards execution - not accumulation.
3. Survival Instinct: Between Attack and Resistance
The fear of defeat triggers visceral reactions: desperate attacks, obsessive defenses, or even premature resignations. But these responses reveal deep truths about human nature:
-
Survival ≠ Violence: A cornered king may shelter behind its pieces, like a strategist choosing patience over confrontation. Is it cowardice or wisdom?
-
The Danger of Ego: Arrogance ("I must win quickly") leads to irreversible mistakes. Humility ("I’ll resist until my opponent errs") can turn certain defeat into salvation.
➡ Reflection: The board doesn’t lie. Every move exposes a player’s deepest instincts: fear, ambition, or temperance.
Online Resources
Check mate patterns - Lichess.org https://lichess.org/practice/checkmates/checkmate-patterns-i/fE4k21MW/9rd7XwOw
Piece check mates - Lichess.org https://lichess.org/practice/checkmates/piece-checkmates-i/BJy6fEDf/8K8FdT6P
Common check mates - Chess.com https://www.chess.com/terms/checkmate-chess
10 fastest check mates - Chess.com https://www.chess.com/article/view/fastest-chess-checkmates
Finding check mates - Chess.com https://www.chess.com/lessons/finding-checkmate
somachess #chess #chesselsalvador #ajedrez #chessphilosophy #philosophy #filosofia #checkmate #longform #article
-
-
 @ f5369849:f34119a0
2025-04-19 05:54:19
@ f5369849:f34119a0
2025-04-19 05:54:19Hackathon Summary
The Build & Brew - Espresso Global Hackathon attracted 485 developers, with 151 projects passing the initial screening. Hosted by Espresso Network, the event distributed $100,000 in prizes over two tracks: "Caffeinate & Code" and "Cracking Composability." The main objectives included enhancing Ethereum's composability and developing new cross-chain applications using Espresso confirmations.
Significant achievements were made, including the deployment of functional rollups integrated with Espresso Network, which supported the development of interoperable applications. Innovations focused on leveraging fast, secure confirmations for cross-chain functionality. Several projects utilized the Open Intents Framework to build advanced application architectures.
The hackathon demonstrated Espresso Network's potential influence on the blockchain ecosystem by applying its consensus layer to real-world scenarios. This event contributed to the network's mission to enable seamless interaction between blockchain chains and highlighted the crucial role of developers in advancing composability. Final pitches, presented on April 7, showcased substantial progress in developing Ethereum's cross-chain capabilities.
Hackathon Winners
Build & Brew Prize Winners
The inaugural Build & Brew hackathon concluded with significant participation from 486 hackers and 156 project submissions. A noteworthy achievement was the successful deployment of 91 Espresso-integrated Arbitrum Orbit chains, paving the way for innovative cross-chain applications. The total prize pool of $65,000 underscored the event's significance, with earnings awarded for Testnet and Mainnet deployments.
Winning Projects
1st Place - Affogato Affogato is a Swap + Bridge system that enhances cross-chain transactions, utilizing Ethereum rollups and Espresso confirmations to ensure secure and efficient exchanges.
2nd Place - Random Network This project enhances composability by using rollup liveness verification and employs an open intents pool for seamless integration across systems.
3rd Place - Disburse Network Disburse Network offers a modular payments protocol enabling one-click, cross-chain mass payments through Nitro rollup architecture, improving payment processing efficiency.
4th Place - Coffee Chain Coffee Chain is a cross-chain payment application that allows merchants to accept crypto payments in any token or blockchain seamlessly.
5th Place - GTXpresso Currently existing as an unfinished placeholder, GTXpresso is a cross-chain Central Limit Order Book (CLOB) project.
To view all projects from the hackathon, visit Build and Brew Hackathon on DoraHacks.
Organization
About the Organizer: Espresso
Espresso is the protocol for coordinated block building: enabling & incentivizing chains to work together as one unified system, and is noted for its expertise in creating efficient, scalable blockchain solutions with an emphasis on security and user accessibility. Key achievements include deploying innovative consensus mechanisms that enhance transaction speed while reducing computational costs. Presently, Espresso is focused on optimizing blockchain infrastructure to drive adoption and support industry-wide digital transformation efforts.
-
 @ df67f9a7:2d4fc200
2025-04-03 19:54:29
@ df67f9a7:2d4fc200
2025-04-03 19:54:29More than just “follows follows” on Nostr, webs of trust algos will ingest increasingly MORE kinds of user generated content in order to map our interactions across the network. Webs of trust will power user discovery, content search, reviews and reccomendations, identity verification, and access to all corners of the Nostr network. Without relying on a central “trust authority” to recommend people and content for us, sovereign Nostr users will make use of “relative trust” scores generated by a wide range of independent apps and services. The problem is, Nostr doesn’t have an opensource library for performing WoT calculations and delivering NIP standard recommendations to users. In order for a “free market” ecosystem of really smart apps and services to thrive, independent developers will need access to extensible “middleware” such as this.
Project Description
I am building a library for independent developers to offer their own interoperable and configurable WoT services and clients. In addition, and as the primary use case, I am also developing a web client for “in person onboarding” to Nostr, which will make use of this library to provide webs of trust recommendations for “invited” users.
-
Meet Me On Nostr (onboarding client) : This is my first project on Nostr, which began a year ago with seed funding from @druid. This web client will leverage “in person” QR invites to generate WoT powered recommendations of follows, apps, and other stuff for new users at their first Nostr touchpoint. The functional MVP release (April ‘25) allows for “instant, anonymous, and fully encrypted” direct messaging and “move in ready” profile creation from a single QR scan.
-
GrapeRank Engine (developer library) : Working with @straycat last fall, I built an opensource and extensible library for Nostr developers to integrate “web of trust” powered reccomendations into their products and services. The real power behind GrapeRank is its “pluggable” interpreter, allowing any kind of content (not just “follows follows”) to be ingested for WoT scoring, and configurable easily by developers as well as end users. This library is currently in v0.1, “generating and storing usable scores”, and doesn’t yet produce NIP standard outputs for Nostr clients.
-
My Grapevine (algo dashboard) : In addition, I’ve just wrapped up the demo release of a web client by which users and developers can explore the power of the GrapeRank Engine.
Potential Impact
Webs of Trust is how Nostr scales. But so far, Nostr implementations have been ad-hoc and primarily client centered, with no consistency and little choice for end users. The “onboarding and discovery” tools I am developing promise to :
-
Establish sovereignty for webs of trust users (supporting a “free market” of algo choices), with opensource libraries by which any developer can easily implement WoT powered recommendations.
-
Accelerate the isolation of bots and bad actors (and improve the “trustiness” of Nostr for everyone else) by streamlining the onboarding of “real world” acquaintances directly into established webs of trust.
-
Improve “discoverability of users and content” for any user on any client (to consume and take advantage of WoT powered recommendations for any use case, even as the NIP standards for this are still in flux), by providing an algo engine with “pluggable” inputs and outputs.
-
Pave the way for “global Nostr adoption”, where WoT powered recommendations (and searches) are consistently available for every user across a wide variety of clients.
Timeline & Milestones
2025 roadmap for “Webs of Trust Onboarding and Discovery” :
-
Meet Me On Nostr (onboarding client) : MVP release : “scan my QR invite to private message me instantly with a ‘move in ready’ account on Nostr”. https://nostrmeet.me/
-
GrapeRank Engine (developer library) : 1.0 release : “expanded inputs and output WoT scores to Nostr NIPs and other stuff” for consumption by clients and relays. https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs
-
My Grapevine (algo dashboard) : 1.0 release : “algo usage and configuration webapp with API endpoints” for end users to setup GrapeRank scoring for consumption by their own clients and relays. https://grapevine.my/
-
Meet Me On Nostr (onboarding client) : 1.0 release : first GrapeRank integration, offering “follow and app recommendations for invited users”, customizable per-invite for Nostr advocates. https://nostrmeet.me/
Prior contributions
-
Last spring I hosted panel discussions and wrote articles on Nostr exploring how to build “sovereign webs of trust”, where end users can have control over which algorithms to use, and what defines “trust”.
-
I contributed gift wrap encryption to NDK.
-
I am also authoring gift wrapped direct messaging and chat room modules for NDK.
-
Last July, I attended The Bitcoin Conference on an OpenSource pass to raise funds for my onboarding client. I onboarded many Bitcoiners to Nostr, and made valuable connections at Bitcoin Park.
About Me
I discovered Nostr in September ‘23 as a freelance web developer, after years of looking for a “sovereignty respecting” social media on which to build apps. With this came my first purchase of Bitcoin. By December of that year, I was settled on “open source freedom tech” (Nostr and Bitcoin) as the new direction for my career.
As a web professional for 20+ years, I know the importance of “proof of work” and being connected. For the last 18 months, I have been establishing myself as a builder in this community. This pivot has not been easy, but it has been rewarding and necessary. After so many years building private tech for other people, I finally have a chance to build freedom tech for everyone. I have finally come home to my peeps and my purpose.
Thank you for considering this application for funding.
-
-
 @ fd208ee8:0fd927c1
2025-02-15 07:37:01
@ fd208ee8:0fd927c1
2025-02-15 07:37:01E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md https://github.com/nostr-protocol/nips/blob/master/61.md
-
 @ 044da344:073a8a0e
2025-04-19 12:00:32
@ 044da344:073a8a0e
2025-04-19 12:00:32Der Chefredakteur war freundlich am Telefon und etwas zerknirscht. Dafür kassieren wir eine Rüge, ganz klar, sagte Hannes Lehner sinngemäß. Er habe mit seiner Redaktion gesprochen, noch einmal an die journalistische Sorgfaltspflicht erinnert, nachzulesen zum Beispiel im Pressekodex des Deutschen Presserates, und die Abläufe so verändert, dass so etwas nicht noch einmal passieren könne. Außerdem sei die Redaktion bereit, mir etwas Gutes zu tun, wenn ich denn eine Idee hätte.
Ich schreibe das hier etwas salopp aus dem Gedächtnis. Hintergrund ist einer dieser üblen Texte, die in der Regionalpresse immer dort aufploppen, wo Menschen öffentlich auftreten, die im kollektiven Gedächtnis gebrandmarkt sind. Querdenker, Putinversteher, Leugner von diesem und jenem. Die Details kann man unten nachlesen und dort auch das Meisterwerk von Andrea Weidemann genießen, immerhin Redaktionsleiterin Plattling-Deggendorf-Osterhofen in der Mediengruppe Attenkofer, die für das Straubinger Tagblatt steht. Veröffentlicht wurde der Text dort am 30. November 2024 auf der Titelseite des Lokalteils in Plattling. Am nächsten Tag habe ich Patrik Baab im Wohnzimmer von Plattling interviewt. Der Saal war voll, trotz oder wegen des Weidemann-Artikels.

Mein Punkt hier ist: Es lohnt sich, solche Angriffe nicht einfach auf sich beruhen zu lassen. Ich hatte es vor zwei Jahren schon einmal versucht beim Presserat und verloren in einer Sache, die viel größer war – mit drei zu zwei Stimmen bei zwei Enthaltungen. Wer weiß. Die Beschwerde ist online, und jeder mag sich selbst ein Urteil bilden. Diesmal war das Urteil auf Ebene eins einstimmig (Beschwerde ist begründet) und auf Ebene zwei fast einstimmig (sechs zu eins): eine Missbilligung, die zwar nicht abgedruckt werden muss, aber in diesem Fall doch sollte („als Ausdruck fairer Berichterstattung“).
Warum es keine Rüge gab, Höchststrafe im Presserat-Kosmos, wissen allein die Götter. Weiter begründet wird das nicht. Das Schreiben des Presserates, immerhin drei eng bedruckte Seiten, wäre ein Thema für sich. Es gelingt den Kollegen dort nicht einmal, den Weidemann-Artikel fehlerfrei zusammenzufassen. So macht mich der Presserat zum Gründer des „Querdenker-Blattes” Demokratischer Widerstand – zu viel der Ehre. Viel wichtiger als irgendwelche Strafen ist aber ohnehin das Gespräch – gerade dort, wo man sich kennt und wo sich jeder Journalist leicht selbst ein Bild machen kann, bevor er in die Tasten haut und Kritiker an den Pranger stellt. Ich bin froh, dass Hannes Lehner zum Telefonhörer gegriffen und auch öffentlich Abbitte geleistet hat, bevor der Presserat sich äußern konnte. Die Zitate, um die es ging, wurden aus der Onlineversion entfernt – genau wie die Bezahlschranke, damit möglichst viele die Entschuldigung sehen. Ich werde dem Chefredakteur vorschlagen, einen seiner Leute zu den nächsten Veranstaltungen der Initiative „Deggendorf miteinander“ zu schicken, und kann mir kaum vorstellen, dass es keine gute Presse gibt, wenn man die Menschen dort erlebt und sich in die Augen gesehen hat.

Beschwerde beim Deutschen Presserat (9. Dezember 2024)
Gegenstand
Diese Beschwerde bezieht sich auf einen Artikel von Andrea Weidemann, der am 30. November 2024 im Plattlinger Anzeiger erschienen ist („Kritiker beantworten kritische Fragen nicht“).
Beschwerdegrund
Der Artikel verstößt gegen die Pressekodex-Ziffern 1, 2 und 9. Die Autorin legt mir zwei wörtliche Zitate in den Mund, die (wenn sie denn wahr wären) nicht nur geeignet sind, meine Ehre zu verletzen (Ziffer 9), sondern es mir auch unmöglich machen würden, weiter als bayerischer Beamter zu wirken. Eine „wahrhaftige Unterrichtung der Öffentlichkeit“ (Ziffer 1) wäre dabei nicht schwer gewesen, wenn Frau Weidemann sorgfältig gearbeitet (Ziffer 2) oder mir die entsprechenden Zitate vor der Veröffentlichung vorgelegt hätte. Es gab vorab einen Mailaustausch (siehe Punkt 3), der sich aber auf etwas ganz anders bezog und mich schon vor der Veröffentlichung daran zweifeln ließ, dass die Ziffern 1 und 2 des Pressekodex Richtschnur des Arbeitens von Andrea Weidemann sind.
Vorgeschichte / Mailaustausch
Für den 1. Dezember 2024 hatte die Initiative „Deggendorf miteinander“ in der Nachbarstadt Plattling eine Buchlesung von Patrik Baab angekündigt und mich gebeten, die Ausführungen des Kollegen wissenschaftlich einzuordnen. Der Titel der Veranstaltung („Wie uns Medien und Lohnschreiber in Kriege treiben“) entsprach dem Untertitel des Buchs „Propaganda-Presse“, das Patrik Baab im Sommer in der Reihe „Hintergrund kompakt“ veröffentlicht hat. Am 27. November erhielt ich folgende Mail:
Sehr geehrter Herr Meyen, in der Hoffnung, dass ich als Mitarbeiterin der Plattlinger Redaktion der Mediengruppe Attenkofer für Sie nicht in die Kategorie „Propaganda-Medium“ falle, hätte ich zu Ihrer Veranstaltungsteilnahme am kommenden Sonntag in Plattling/Niederbayern folgende Fragen: 1. Auf der Suche nach näheren Informationen zu Ihrer Person habe ich mehrfach gelesen, dass Sie der Ansicht sind, dass die (Leit-)Medien bewusst auf die Gesellschaft Einfluss nehmen, also manipulieren. Welche Belege haben Sie dafür? Und: Gilt das Ihrer Ansicht nach für alle Medien? Und für alle Themenbereiche? 2. Auch haben Sie sich kritisch zu journalistischen Faktencheckern geäußert und Sie als Propagandamaschinen bezeichnet. Heißt das, dass auch Medien wie z.B. Correctiv Ihrer Meinung nach nicht glaubwürdig sind? 3. Wenn man heute von Medien spricht, muss man vor allem das Internet im Blick behalten. Ist es nicht so, dass gerade dort ungefilterte (Falsch-)Informationen verbreitet werden? Für eine zeitnahe Rückmeldung wäre ich Ihnen sehr dankbar. Mit besten Grüßen, Andrea Weidemann, Redaktionsleitung Plattling-Deggendorf-Osterhofen
Eine solche Beschwerde ist nicht der Ort, sich im Detail mit diesen Fragen auseinanderzusetzen. Ich will deshalb nur darauf hinweisen, dass es hier schlicht keine vernünftigen Antworten gab. Frage 1 beschreibt gewissermaßen die Geschäftsgrundlage von Journalismus und Medienforschung. Wenn man nicht von Wirkungen ausgehen würde, könnten sich beide Berufsgruppen die Arbeit sparen. Zum Thema „Glaubwürdigkeit der Medien“ (Frage 2) habe ich mich 2001 habilitiert und schon seinerzeit darauf hingewiesen, dass es sich hierbei um keine sinnvolle Kategorie für die Bewertung journalistischer Leistungen handelt. Frage 3 ist suggestiv und so allgemein formuliert, dass eigentlich nur ein „Ja“ möglich ist. Ich habe deshalb am nächsten Morgen eher ironisch geantwortet und die Kollegin zugleich an die Berufstugenden erinnert:
Was soll ich dazu sagen, liebe Andrea Weidemann? Sie finden im Internet komische Sachen über mich und fragen dann, ob dort Falschinfos verbreitet werden. Am besten (das ist ja auch das Credo von Patrik Baab): Sie kommen am Sonntag und machen sich selbst ein Bild. Bis dahin mit den besten Grüßen
Antwort:
Sehr geehrter Herr Meyen, natürlich werde ich am Sonntag anwesend sein. Trotzdem schade, dass sie auf meine Fragen nicht antworten. Ich habe keine „komischen Sachen“ gelesen, sondern konkrete Aussagen von Ihnen zitiert. Darf ich noch mit einer Stellungnahme rechnen?
Frau Weidemann war dann nicht bei der Veranstaltung, hat aber vorab den Artikel veröffentlicht, über den ich mich hier beschwere.
Falschzitate
Beide Zitate befinden sich im vierten Absatz des Artikels, der offensichtlich darauf abzielt, ein „Porträt“ von Michael Meyen zu liefern. Dass mein Leben und mehr als 20 Jahre auf einer Professur für Kommunikationswissenschaft an der LMU München dabei auf die beiden Ausgaben der Wochenzeitung Demokratischer Widerstand (DW) reduziert werden, in denen ich als einer von vier „Herausgebern“ genannt werde, mag schlechter Stil sein. Wenn allerdings mit Anführungszeichen (also als wörtliches Zitat markiert) behauptet wird, ich hätte Deutschland als „Spritzenmörder-Diktatur“ bezeichnet, hört der Spaß auf. Ich habe im März 2002 einen Eid auf die bayerische Verfassung geschworen und würde mich mit einer solchen Aussage selbst ins Abseits stellen und meine berufliche Zukunft aufs Spiel setzen. Dazu kommt, dass der Plattlinger Anzeiger in einer Region erscheint, die seit mehr als dreieinhalb Jahren meine Wahlheimat ist. Eine solche Falschberichterstattung ist so geeignet, meine Reputation auch über mein berufliches Wirken hinaus nachhaltig zu beschädigen.
Das gilt so in etwas abgeschwächter Form auch für das zweite Zitat. Nach einer Zusammenfassung zum Wirken besagter Wochenzeitung folgt „Meyens Meinung“, wieder in Anführungszeichen und mir damit wortwörtlich in den Mund gelegt: „Die Medien haben sich der Propaganda der NATO vollumfänglich unterworfen.“
Ich kann nur mutmaßen, von wem beide Zitate stammen. „Propaganda der NATO“ ist nicht mein Thema, Pauschalisierungen wie „die Medien“ liegen mir fern, und ich würde den Teufel tun, die Bundesrepublik Deutschland als „Diktatur“ zu bezeichnen oder das Wort „Spritzenmörder“ in den Mund zu nehmen (wie auch das Wort „vollumfänglich“, aber das nur am Rande). Falls beide Zitate im DW gestanden haben sollten: Ich habe meine „Beziehung“ zu dieser Wochenzeitung in einem Buch behandelt (Wie ich meine Uni verlor, 2023) und außerdem eine Stellungnahme veröffentlicht (In eigener Sache, 9. Mai 2024).
Dort steht auch, dass ich gegen die Disziplinarstrafe klage, von der Andrea Weidemann zu berichten weiß (verhängt allerdings nicht „von der LMU“, sondern von der Landesanwaltschaft, einer internen Ermittlungsbehörde). Das Verfahren läuft noch. Die Kürzung der „Bezüge um zehn Prozent“ ist folglich ausgesetzt. Ich könnte mich hier also auch wegen eines Verstoßes gegen Ziffer 13 beschweren.
Zusammengefasst: Andrea Weidemann zielt mit ihrem Text darauf ab, meine Ehre zu verletzen, meine Reputation in Frage zu stellen und die Leser ihrer Zeitung so davon abzuhalten, die Lesung von Patrik Baab am folgenden Tag zu besuchen. Die Autorin legt mir dazu zwei Zitate in den Mund, die nicht von mir stammen. Statt diese Zitate von mir bestätigen zu lassen, schickt sie in einer Mail das, was sie offenbar unter „kritischen Fragen“ versteht (Überschrift des Artikels), und wundert sich dann auch noch, dass es darauf keine Antworten gibt. Der Beitrag verstößt gegen die Ziffern 1, 2 und 9 des Pressekodex und würde auch bei Ziffer 13 einer näheren Prüfung nicht standhalten.

-
 @ f5369849:f34119a0
2025-04-19 05:54:02
@ f5369849:f34119a0
2025-04-19 05:54:02Hackathon Summary
The Injective AI Agent Hackathon, presented by Injective and ElizaOS, wrapped up with 126 approved project submissions developed by 496 participants. This hackathon highlighted the integration of AI and blockchain, showcasing the potential for AI agents to operate within decentralized networks and drive innovation beyond traditional finance. Participants explored various applications, including autonomous trading, tokenized asset management, and AI-driven financial insights.
A prize pool of up to $100,000 was up for grabs, with a $50,000 grand prizes and additional awards for other notable projects. By merging AI's adaptability with blockchain's transparency, the hackathon demonstrated the transformative potential of these technologies and marked a significant milestone in showcasing the innovative potential of AI and blockchain integration.
Hackathon Winners
Grand Prize
Jecta: Jecta integrates multiple large language models (LLMs) to automate tasks on the Injective blockchain. It focuses on transparency and community-driven development, utilizing open-source technology to enhance ease of use and efficiency.
Paradyze: Paradyze improves the Injective ecosystem by incorporating natural language interfaces for blockchain transactions. Its design aims to enhance accessibility and security, allowing users straightforward interaction methods.
To view all projects, visit the Injective AI Hackathon page.
About the Organizer: Injective
Injective is the high-performance blockchain for finance, offering unmatched speed, scalability, and advanced infrastructure to power the future of on-chain applications.
Injective's mission is to advance financial freedom by providing accessible and reliable decentralized infrastructure for diverse financial services, empowering both users and developers to innovate within the blockchain ecosystem.
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-16 13:27:53
@ 5d4b6c8d:8a1c1ee3
2025-04-16 13:27:53https://primal.net/e/nevent1qvzqqqqqqypzqntcggz30qhq60ltqdx32zku9d46unhrkjtcv7fml7jx3dh4h94nqqszw6rqxppmm48pvvc5pz4q74r7qvsgl8tzwfgp3kqg82jw04t2n3q2nrlqh
Get used to and comfortable with being responsible for your own wellbeing.
originally posted at https://stacker.news/items/945039
-
 @ 502ab02a:a2860397
2025-04-19 05:39:36
@ 502ab02a:a2860397
2025-04-19 05:39:36น้ำมันถั่วเหลือง ของเหลวสีทองในครัว... แต่ในเซลล์เราอาจไม่ขำ หลายบ้านรักน้ำมันถั่วเหลือง เพราะมัน... -หาง่าย -ราคาน่ารัก -ผัดอะไรก็หอมเบา ๆ แบบบ้าน ๆ แถมบางแบรนด์ยังใส่ฉลาก “มีโอเมกา 3” ให้ดูดีในชั้นวางซูเปอร์ เหมือนกำลังได้กินแซลมอนแบบขวด ใช่ครับ ในน้ำมันถั่วเหลืองมีโอเมกา 3 จริง แต่เป็นชนิด ALA (Alpha-Linolenic Acid) ซึ่งร่างกายเราจะต้องแปลงเป็น DHA/EPA ถึงจะใช้งานได้ ปัญหาคือ... อัตราแปลงต่ำเตี้ยเรี่ยดิน แค่ 0.5–5% เท่านั้น
แถมปริมาณโอเมกา 6 ยังสูงจนเบียดโอเมกา 3 ตกเวที แล้วความสมดุลของกรดไขมันทั้งสองสายนี้ คือหัวใจสำคัญของการควบคุม การอักเสบ (inflammation) โอเมกา 3 = ดับไฟ โอเมกา 6 = จุดไฟ แต่น้ำมันถั่วเหลืองใส่ชุดนักผจญเพลิงมา แต่ดันถือไฟแช็คอะ
โอเมกา 6 + ความร้อน = สารพิษในครัว เมื่อเอาน้ำมันถั่วเหลืองไปเจอไฟสูง ๆ จากการผัดหรือทอด จะเกิด lipid peroxidation – ปฏิกิริยาออกซิเดชันที่เปลี่ยนไขมันดี ๆ ให้กลายเป็น สารอนุมูลอิสระสุดร้าย สารเหล่านี้สามารถไปทำลายเยื่อหุ้มเซลล์ ทำให้เกิดการอักเสบในระดับเซลล์เรื้อรัง ไม่ทันรู้ตัว ก็มีอาการปวดเมื่อย ตับอักเสบ ไขมันเกาะตับ หรือแม้กระทั่งภูมิคุ้มกันล้มเหลวแบบไม่ได้เชิญหมอดูมาก่อน
ปริมาณ PUFA (polyunsaturated fatty acids) สูงถึงกว่า 50-60% ซึ่งในสภาพของธรรมชาติ PUFA ไม่ได้ร้าย… แต่เมื่อมันถูกนำไปเจอไฟแรงๆ เช่น ทอด ผัด หรือแม้แต่ผ่านกระบวนการ refine ที่อุณหภูมิสูง มันจะกลายเป็น ไขมันไม่เสถียร ที่เหมือนคนใจบาง เจออะไรแรงๆ ไม่ได้เลย เพราะจะเกิดสาร lipid peroxidation products ที่ทำลายเซลล์ ตับ หลอดเลือด และอวัยวะที่คุณรักอย่างไม่รู้ตัว
ถั่วเหลืองยุคนี้... ไม่เหมือนเมื่อก่อน ถ้าถั่วเหลืองเมื่อก่อน อาจจะเป็นคุณป้าผู้รักสุขภาพ ถั่วเหลืองยุค GMO ก็อาจเป็น influencer สายปลอมที่แต่งหน้าหนักด้วย glyphosate น้ำมันถั่วเหลืองในตลาดส่วนใหญ่สกัดจากถั่วเหลือง GMO ผ่านการใช้ตัวทำละลายอย่าง เฮกเซน (hexane) ซึ่งแม้จะมีประสิทธิภาพในการรีดน้ำมันจากวัตถุดิบอย่างยอดเยี่ยม แต่ก็มีข่าววิจัยมากมายที่เริ่มตั้งคำถามว่า เฮกเซนตกค้างหรือไม่ และถ้าตกค้าง จะมีผลต่อระบบประสาทหรือไม่? และกระบวนการทำให้ใสที่ต้องใช้ ความร้อนและเคมีอีกหลายขั้น ซึ่งแน่นอนว่า... ไขมันที่ร่างกายเราควรได้รับ ควรเป็นไขมันที่เรียบง่าย ดิบ ๆ ดั้งเดิม ไม่ใช่ไขมันที่ถูก “ฟอกสี เติมกลิ่น กรองเคมี” จนแทบไม่เหลือความเป็น real food
แต่น้ำมันถั่วเหลืองก็มีข้อดีนะ น้ำมันถั่วเหลืองที่ไม่ได้ refine จนหมดเกลี้ยง ถ้าไม่ได้ปรุงด้วยความร้อนจะยังคงวิตามินอีไว้พอสมควร ซึ่งเป็นสารต้านอนุมูลอิสระที่ดีต่อผิวพรรณและช่วยลดการเกิด oxidative stress ได้ นอกจากนี้ยังเป็นที่นิยมเพราะมีราคาถูก สะดวก หาง่าย และรสชาติไม่กลบวัตถุดิบ จึงเป็นที่นิยมในอุตสาหกรรมอาหารและเบเกอรี่ เช่น ขนมปัง มายองเนส หรือสินค้าจำพวกแปรรูปต่างๆ
นั่นหมายความว่า เป็นอีกหนึ่งน้ำมันที่เหมาะกับการนำไปทำ ultra processed food เชียวครับ ได้ต้นทุนที่สะดวกและหาง่ายด้วย เป็นน้ำมันหลักในการทำ มายองเนส เลยครับ
และคำถามสำคัญที่น่าจะมีมาด้วย ตอบไว้ก่อนเลยครับว่า น้ำมันถั่วเหลือง ไม่มีสารแกมมา-โอริซานอล (γ-Oryzanol) จ้ะ แพ้น้ำมันรำข้าวเด้อ #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 7bdef7be:784a5805
2025-04-02 12:37:35
@ 7bdef7be:784a5805
2025-04-02 12:37:35The following script try, using nak, to find out the last ten people who have followed a
target_pubkey, sorted by the most recent. It's possibile to shortensearch_timerangeto speed up the search.```
!/usr/bin/env fish
Target pubkey we're looking for in the tags
set target_pubkey "6e468422dfb74a5738702a8823b9b28168abab8655faacb6853cd0ee15deee93"
set current_time (date +%s) set search_timerange (math $current_time - 600) # 24 hours = 86400 seconds
set pubkeys (nak req --kind 3 -s $search_timerange wss://relay.damus.io/ wss://nos.lol/ 2>/dev/null | \ jq -r --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[] | select(.[0] == "p" and .[1] == $target)) | .pubkey ' | sort -u)
if test -z "$pubkeys" exit 1 end
set all_events "" set extended_search_timerange (math $current_time - 31536000) # One year
for pubkey in $pubkeys echo "Checking $pubkey" set events (nak req --author $pubkey -l 5 -k 3 -s $extended_search_timerange wss://relay.damus.io wss://nos.lol 2>/dev/null | \ jq -c --arg target "$target_pubkey" ' select(. != null and type == "object" and has("tags")) | select(.tags[][] == $target) ' 2>/dev/null)
set count (echo "$events" | jq -s 'length') if test "$count" -eq 1 set all_events $all_events $events endend
if test -n "$all_events" echo -e "Last people following $target_pubkey:" echo -e ""
set sorted_events (printf "%s\n" $all_events | jq -r -s ' unique_by(.id) | sort_by(-.created_at) | .[] | @json ') for event in $sorted_events set npub (echo $event | jq -r '.pubkey' | nak encode npub) set created_at (echo $event | jq -r '.created_at') if test (uname) = "Darwin" set follow_date (date -r "$created_at" "+%Y-%m-%d %H:%M") else set follow_date (date -d @"$created_at" "+%Y-%m-%d %H:%M") end echo "$follow_date - $npub" endend ```
-
 @ da0b9bc3:4e30a4a9
2025-04-16 08:28:24
@ da0b9bc3:4e30a4a9
2025-04-16 08:28:24Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/944844
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ 502ab02a:a2860397
2025-04-19 05:28:40
@ 502ab02a:a2860397
2025-04-19 05:28:40ตัวหนังสือมีเสียง วันนี้แซงมาเพลงนึง
เพลงนี้ชื่อ "เสมอ" เป็นเพลงที่ผมเขียนขึ้นมาเพื่อเหตุผล 2 อย่าง 1. อยากมีเพลงเกี่ยวกับแดด ไว้รองรับ content ตากแดด 2. อยากมีเพลงปลอบประโลมใจ เพราะตกตะกอนมาจากโพส "แตกสลายเพื่อเติบโต"
สองเหตุผลนี้มันสอดคล้องกันดีครับ สามารถเป็นเพลงเดียวกันได้ เพราะเพลงเกี่ยวกับแดด ผมไม่อยากได้เนื้อหาแบบ วิตามินดี ส่งเสริมร่างกายแข็งแรง แบบเพลงเต้นประกอบท่าตอนเช้า 5555 คนละจุดมุ่งหมายกัน
ท่อนย้ำผมเลยใช้คำว่า "พรุ่งนี้จะมาใหม่ พรุ่งนี้จะมาใหม่ เสมอ..." แล้วเล่นคำย้ำซ้ำว่า "พรุ่งนี้จะสู้ใหม่ พรุ่งนี้จะสู้ใหม่ นะเธอ..." ใครตามงานผมน่าจะพอทราบลายเซนต์ว่า สไตล์นี้นี่กูเลย 5555
เพลงจะเล่าถึงความอ่อนล้า ที่เทียบกับคืนอันหนาวเย็น โดดเดี่ยว แต่เมื่อไหร่ที่แดดสาดส่อง นอกจากความมืดจะหายไปแล้ว ความอบอุ่น การเริ่มต้นใหม่ ก็แสดงตัวตนว่ากำลังมาหา
สิ่งนึงที่อยากให้จำไว้เสมอคือ "พระอาทิตย์ จะขึ้นทิศทางเดิมเสมอ" เมื่อไหร่ที่อ่อนล้า เมื่อยใจ ไร้กำลัง ให้รู้ว่า พรุ่งนี้นะ พรุ่งนี้ พระอาทิตย์จะมาโอบกอดเธอด้วยความอบอุ่น แบบที่เป็น "เสมอ"
บทความเกี่ยวกับแดดพรุ่งนี้ ก็มีความสอดคล้องกับเพลงนี้ครับ ไว้ติดตามอ่านกันตอนตากแดด พรุ่งนี้ 8.00 นะครับ
อ้อ เพลงนี้ไม่ได้ลงในระบบใดทั้งสิ้น (เพราะยังไม่ได้เอาไปลง 555) มันจึงมีความพิเศษที่ ฟังได้ที่นี่เท่านั้นครับ แก้ๆๆ ลืมหว่ะ youtube มี https://youtu.be/esyd_W_gyZ0?si=kH7gVod3vd1b16Qq 55555
เนื้อเพลง "เสมอ" Song by : HereTong Teera Siri เหนื่อยล้าอ่อนแรง มืดมนแค่ไหน โดดเดี่ยวเพียงใด หัวใจอ่อนล้า
ผ่านวันนี้ ไปด้วยกัน ผ่านวันนี้ ไปด้วยความฝัน
พรุ่งนี้จะมาใหม่ พรุ่งนี้จะมาใหม่ เสมอ...
เมื่ออาทิตย์สาดแสง ความมืดจะจางหาย ความหนาวจะกลับกลาย ได้ไออุ่น
เมื่ออาทิตย์ส่องแสง หัวใจจะเริ่มคุ้น ความละมุนแห่งรัก ให้พักใจ
โลกสวยสดใส สว่างไสวสุดฟ้า ใจที่อ่อนล้า ละลายหายไป
ผ่านวันนี้ไปด้วยกัน ผ่านวันนี้ไปพร้อมกับฝัน แล้วพรุ่งนี้จะสู้ใหม่ พรุ่งนี้จะสู้ใหม่ นะเธอ...
ใต้อาทิตย์สาดแสง เรี่ยวแรง เติมเต็มหมดใจ แสงจะส่องไป สู่ปลายทาง แห่งความฝัน สู้วันนี้ไปด้วยกัน สู้วันนี้ไป ด้วยความฝัน เธอยังมีฉันเสมอ เพียงเธอมองบนฟ้า... พรุ่งนี้ฉัน จะมาใหม่ เสมอ...
pirateketo #sundayspecialเราจะไปเป็นหมูแดดเดียว #siripun #ตำรับเอ๋
-
 @ 72103ac9:460b37fd
2025-04-19 05:01:34
@ 72103ac9:460b37fd
2025-04-19 05:01:34Se você está em busca de uma plataforma moderna, segura e recheada de opções para se divertir online, a 7788bet é a escolha perfeita. Com uma interface intuitiva, suporte ao jogador de alta qualidade e uma ampla gama de jogos emocionantes, a 7788bet se destaca como um dos principais nomes no entretenimento digital do Brasil. Vamos explorar mais sobre essa plataforma inovadora e o que a torna tão especial.
Uma Plataforma Feita Para o Jogador Brasileiro A 7788bet foi pensada para atender as necessidades do público brasileiro, oferecendo não só suporte em português, mas também métodos de pagamento locais que facilitam o acesso e tornam toda a experiência mais prática. Com navegação rápida e visual moderno, o site proporciona uma experiência agradável tanto em computadores quanto em dispositivos móveis.
Desde o momento do cadastro até a hora de sacar seus ganhos, tudo é feito com segurança e transparência. A plataforma investe em tecnologia de ponta para garantir que seus dados estejam sempre protegidos, além de manter políticas rígidas de privacidade e jogo responsável.
Diversidade de Jogos para Todos os Gostos Uma das maiores vantagens da 7788bet é a sua biblioteca de jogos, que abrange desde os clássicos até os lançamentos mais modernos. Aqui, os jogadores encontram:
Slots Temáticos: Com gráficos impressionantes, trilhas sonoras imersivas e diversas mecânicas de bônus, os slots são ideais para quem gosta de jogos dinâmicos e recheados de surpresas.
Jogos de Mesa Virtuais: Os tradicionais jogos de cartas e roleta ganham versões virtuais de alta qualidade, oferecendo uma jogabilidade fluida e intuitiva.
Esportes Virtuais: Para quem gosta de esportes e quer experimentar algo diferente, os esportes virtuais simulam partidas com resultados aleatórios, trazendo uma nova camada de emoção.
Jogos Ao Vivo: Os jogos ao vivo colocam você frente a frente com anfitriões reais, transmitidos em tempo real, o que proporciona uma experiência mais interativa e autêntica.
Cada jogo é desenvolvido por provedores renomados, garantindo não apenas qualidade gráfica e sonora, mas também justiça nos resultados, certificados por entidades independentes.
Experiência do Jogador: Tudo Gira em Torno da Diversão Na 7788bet, o foco principal é proporcionar uma experiência prazerosa para seus usuários. Isso se reflete em diversas áreas, como:
Bônus e Promoções Frequentes: Novos usuários são recebidos com bônus de boas-vindas atrativos, e os jogadores fiéis podem aproveitar promoções semanais e programas de fidelidade com recompensas especiais.
Atendimento ao Cliente de Excelência: A equipe de suporte está disponível 24 horas por dia, 7 dias por semana, pronta para resolver qualquer dúvida ou problema de forma rápida e eficiente, sempre com simpatia e profissionalismo.
Depósitos e Saques Rápidos: A plataforma trabalha com os principais métodos de pagamento do país, garantindo que seus depósitos sejam instantâneos e os saques sejam processados com agilidade.
Além disso, o ambiente é completamente adaptado para o público brasileiro, com uma linguagem acessível e promoções específicas para o mercado nacional, o que torna tudo mais familiar e convidativo.
Conclusão A 7788bet é muito mais do que uma simples plataforma de jogos online. É um ambiente completo de entretenimento, pensado para oferecer segurança, diversão e praticidade para jogadores de todos os perfis. Se você procura uma experiência diferenciada, com muitas opções de jogos, suporte eficiente e uma comunidade crescente de jogadores satisfeitos, a 7788bet é o lugar ideal para começar sua jornada.
-
 @ 7bdef7be:784a5805
2025-04-02 12:12:12
@ 7bdef7be:784a5805
2025-04-02 12:12:12We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs.
The problem
Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so everyone can actually snoop what we are interested in, and what is supposable that we read daily.
The solution
Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see NIP-51). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also really private one.
One might wonder what use can really be made of private lists; here are some examples:
- Browse “can't miss” content from users I consider a priority;
- Supervise competitors or adversarial parts;
- Monitor sensible topics (tags);
- Following someone without being publicly associated with them, as this may be undesirable;
The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of how many bots scan our actions to profile us.
The current state
Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff (NIP-44). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply mark them as local-only, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment.
To date, as far as I know, the best client with list management is Gossip, which permits to manage both encrypted and local-only lists.
Beg your Nostr client to implement private lists!
-
 @ c066aac5:6a41a034
2025-04-15 22:06:06
@ c066aac5:6a41a034
2025-04-15 22:06:06-Interpretive ~~loops~~ Technology Poetry by Zachariah Sanders
I am testing ~~the loops~~Comet.
It fit many loop It has many features.~~There are loops~~ There are cool tools.
I mean, like, really cool;
I'm going to embed ~~the loops~~ a video that lives rent free in my mind:
https://www.youtube.com/watch?v=peXNAwzyJas
Anyway, long live innovation!
~~Long live the loops~~
https://github.com/nodetec/comet
loops #comet #article #nostrinnovation #nostr #willzap4loops
-
 @ 72103ac9:460b37fd
2025-04-19 05:00:55
@ 72103ac9:460b37fd
2025-04-19 05:00:55Se você está em busca de uma plataforma online completa, segura e cheia de emoção, a 136bet é a escolha perfeita. Com um ambiente moderno, interface amigável e uma grande variedade de jogos eletrizantes, a plataforma se destaca como uma das preferidas entre os jogadores brasileiros. Desde sua chegada ao mercado, a 136bet tem conquistado a confiança e o coração dos usuários graças à sua seriedade, suporte de qualidade e experiência imersiva.
Uma Plataforma Completa e Segura A 136bet foi desenvolvida com tecnologia de ponta para garantir segurança, estabilidade e acessibilidade aos jogadores. Seu sistema de cadastro é rápido e intuitivo, e as transações financeiras são protegidas com protocolos de criptografia avançados, oferecendo total tranquilidade aos usuários. Outro diferencial é o suporte ao cliente, disponível 24 horas por dia, todos os dias da semana, com atendimento em português para solucionar dúvidas e oferecer suporte técnico sempre que necessário.
A navegação pelo site é fluida e prática, tanto em computadores quanto em dispositivos móveis. Isso permite que o jogador possa se divertir de qualquer lugar, seja em casa, no trabalho ou durante uma viagem.
Variedade de Jogos para Todos os Gostos Na 136bet, a diversão é garantida com uma ampla seleção de jogos que atendem a todos os perfis de jogador. Entre os destaques da plataforma estão:
Jogos de cartas ao vivo: clássicos como pôquer, bacará e blackjack são oferecidos em tempo real, com crupiês profissionais e interatividade de alto nível.
Roletas dinâmicas: diferentes versões da roleta estão disponíveis, com animações envolventes e mecânicas variadas para proporcionar uma experiência sempre renovada.
Slots modernos: os populares jogos de giro estão presentes em abundância, com temas diversos, gráficos de alta qualidade e bônus emocionantes que aumentam as chances de vitória.
Esportes virtuais e apostas esportivas: para quem curte esportes, a plataforma também oferece apostas em partidas ao vivo e jogos simulados com inteligência artificial de última geração.
Todos os jogos são fornecidos por desenvolvedores renomados do mercado internacional, garantindo qualidade gráfica, fluidez e total justiça nos resultados.
Experiência de Jogador Inesquecível O grande trunfo da 136bet está na experiência que proporciona aos seus usuários. Tudo foi pensado para que o jogador se sinta confortável, confiante e valorizado. Promoções frequentes, torneios interativos e programas de fidelidade são apenas algumas das vantagens disponíveis.
Além disso, o sistema de recompensas é bastante atrativo. Os usuários acumulam pontos à medida que jogam, podendo trocá-los por prêmios, bônus ou vantagens exclusivas. Isso cria um senso de progresso e motivação constante.
Outro ponto importante é a personalização. A plataforma adapta sugestões de jogos com base nas preferências do usuário, criando uma experiência única e sob medida para cada perfil.
Conclusão A 136bet é muito mais do que uma simples plataforma de entretenimento online. Ela oferece uma combinação ideal de segurança, variedade e emoção, colocando o jogador no centro da experiência. Com jogos envolventes, suporte eficiente e promoções vantajosas, a plataforma se consolida como uma das melhores opções do mercado brasileiro.
Se você ainda não conhece a 136bet, essa é a hora de explorar um novo universo de diversão e recompensas. Cadastre-se hoje mesmo e descubra tudo o que essa plataforma inovadora tem a oferecer!
-
 @ 72103ac9:460b37fd
2025-04-19 05:00:14
@ 72103ac9:460b37fd
2025-04-19 05:00:14A R8Bet vem se destacando como uma das plataformas de entretenimento online mais completas e confiáveis do Brasil. Com um visual moderno, sistema intuitivo e uma gama variada de jogos, a R8Bet oferece uma experiência única para jogadores de todos os perfis, desde iniciantes até os mais experientes.
Uma Plataforma Feita para o Jogador Brasileiro Desde o primeiro acesso, é fácil perceber que a R8Bet foi desenvolvida pensando nas necessidades do público brasileiro. O site é totalmente otimizado em português, com suporte ao cliente disponível 24 horas por dia, 7 dias por semana, pronto para responder dúvidas e resolver qualquer questão com agilidade e cordialidade.
Além disso, a plataforma conta com métodos de pagamento populares no Brasil, como PIX, boleto bancário e carteiras digitais, facilitando os depósitos e saques de forma rápida e segura. Isso demonstra o compromisso da R8Bet em proporcionar uma experiência prática e eficiente do começo ao fim.
Variedade de Jogos para Todos os Gostos Um dos grandes diferenciais da R8bet é sua ampla seleção de jogos, que abrange desde clássicos do entretenimento digital até lançamentos modernos e interativos. A plataforma trabalha com os principais provedores do mercado, garantindo gráficos de alta qualidade, jogabilidade fluida e muita diversão.
Entre os destaques, estão os jogos de roleta online, onde a emoção gira em torno de cada número sorteado; os títulos de cartas, como poker e blackjack, que exigem estratégia e atenção; além das famosas slots, que trazem temas variados, animações incríveis e bônus empolgantes. A cada clique, o jogador encontra novas possibilidades de se entreter e até mesmo de lucrar com suas habilidades.
Experiência Imersiva e Segura A R8Bet não se limita apenas à variedade. A plataforma investe constantemente em tecnologia de ponta para garantir um ambiente seguro e justo para todos os usuários. Todos os jogos utilizam sistemas certificados de geração aleatória de resultados, assegurando transparência nas rodadas e confiança nos resultados.
O design responsivo do site permite que os jogos sejam acessados tanto pelo computador quanto por dispositivos móveis, sem perda de qualidade. Isso significa que o usuário pode jogar de onde quiser, a qualquer hora, mantendo a emoção sempre ao seu alcance.
Outro ponto positivo é o sistema de recompensas e promoções. A R8Bet oferece bônus de boas-vindas, promoções recorrentes e programas de fidelidade para os jogadores mais assíduos. Esses incentivos tornam a experiência ainda mais envolvente, aumentando as chances de ganhos e premiando a lealdade dos usuários.
Comunidade Ativa e Atendimento de Qualidade A R8Bet valoriza o relacionamento com seus usuários e mantém uma comunidade ativa, onde os jogadores podem interagir, trocar dicas e acompanhar as novidades. A plataforma também está presente nas redes sociais, compartilhando conteúdos relevantes, promoções exclusivas e atualizações constantes sobre os jogos.
O atendimento ao cliente é outro destaque. Equipes treinadas estão disponíveis para auxiliar via chat ao vivo, e-mail ou redes sociais, sempre com foco na satisfação e bem-estar do usuário. A rapidez nas respostas e a eficiência nas soluções reforçam a confiabilidade da marca no cenário brasileiro.
Conclusão A R8Bet é, sem dúvida, uma escolha inteligente para quem busca diversão de qualidade, segurança e uma experiência completa de entretenimento online. Com sua plataforma intuitiva, catálogo variado de jogos, suporte dedicado e recompensas atrativas, a R8Bet se consolida como uma das líderes no mercado nacional.
Se você procura emoção, praticidade e a chance de transformar cada jogada em uma grande conquista, a R8Bet é o lugar ideal para começar essa jornada. Experimente hoje mesmo e descubra um novo nível de entretenimento!
-
 @ e968e50b:db2a803a
2025-04-15 17:45:27
@ e968e50b:db2a803a
2025-04-15 17:45:27Hey cinephiles, I'm just crossposting this bounty that remains unclaimed from last week. It occurred to me that you may be a more receptive audience to this game that I made than the folks monitoring the gamers territory. Either way, let me know what you think. I've been told it's too hard...but maybe not for you!
https://stacker.news/items/937363
originally posted at https://stacker.news/items/944303
-
 @ fd78c37f:a0ec0833
2025-04-01 11:49:06
@ fd78c37f:a0ec0833
2025-04-01 11:49:06In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin.
YakiHonne: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community.
Keypleb:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here.
YakiHonne: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin?
Keypleb:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one.. Keypleb:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began. Keypleb:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.

YakiHonne: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way?
Keypleb:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge. Keypleb:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue. Keypleb:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.
 YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?
YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?Keypleb:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup. Keypleb:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys. Keypleb:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community.
YakiHonne: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both?
Keypleb:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content. Keypleb:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin. Keypleb:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure. Keypleb:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon. Keypleb:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.
 YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?
YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?Keypleb:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.
 Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.
Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.YakiHonne: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems? Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses.
Keypleb:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area. Keypleb:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption. Keypleb:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that.
YakiHonne: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment?
Keypleb:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds. Keypleb:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again. Keypleb:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future.
YakiHonne: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided.
Keypleb:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again.
Bitcoin Indonesia nostr: nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3
Keypleb nostr: nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx
-
 @ 75869cfa:76819987
2025-04-01 05:55:38
@ 75869cfa:76819987
2025-04-01 05:55:38GM, Nostriches!
The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review:
In the past two weeks, Nostr statistics indicate over 221,000 daily trusted pubkey events. The number of new users has seen a notable decrease, with profiles containing a contact list dropping by 79%. More than 10 million events have been published, reflecting a 12% decrease. Total Zap activity stands at approximately 21 million, marking a 15% increase.
Additionally, 15 pull requests were submitted to the Nostr protocol, with 2 merged. A total of 45 Nostr projects were tracked, with 8 releasing product updates, and over 569 long-form articles were published, 24% focusing on Bitcoin and Nostr. During this period, 7 notable events took place, and 2 significant events are upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 221,000, representing a slight 8 % decrease compared to the previous period. Daily activity peaked at 17662 events, with a low of approximately 15781.
The number of new users has decreased significantly. Profiles with bio are now around 25951, reflecting a 79% drop. Pubkeys writing events have decreased by 50% compared to the previous period.
Regarding event publishing, all metrics have shown a decline. The total number of note events published is around 10 million, reflecting a 12% decrease. Posts remain the most dominant in terms of volume, totaling approximately 1.7 million, which is a 4.4 % decrease. Both reposts and reactions have decreased by about 5%.
For zap activity, the total zap amount is about 21 million, showing an increase of over 15% compared to the previous period.
Data source: https://stats.nostr.band/
NIPs
Added optional signString() method
nostr:npub1emq0gngdvntdn4apepxrxr65vln49nytqe0hyr58fg9768z5zmfqcwa3jz is proposing a signString() method that allow Nostr users to sign/authenticate messages for external apps without compromising their private key (nsec).It opens up a more generic and flexible challenge-response style external authentication method, using the same Schnorr signature mechanism that Nostr uses to sign events natively.External apps need only understand Schnorr signatures - they do not need to understand Nostr's event structure. This widens interoperability.A concrete example of where this would be useful is P2PK locking of Cashu ecash tokens to a Nostr pubkey (npub). Decoding the token requires a Scnorr signature on a structured message string. This method would allow a signer to handle It cleanly.
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 defines kind:39701 as website bookmarks.Bookmarks can be queried by the d tag, which is just their URL without the scheme, which is always and everywhere assumed to be https://. The querystring and the hash must be removed entirely, unless their requirement is explicitly stated either by the user or by some hardcoded list of URLs that rely on query strings for basic routing provided by the client (I've searched the internet extensively and could only find 3 websites that do this: YouTube, Hacker News and a random guy's sad old blog). Bookmarks can be commented on with NIP-22.
nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that covers the inclusion of Progress Events as implemented in Open Librarian. While the specific implementation is focused on tracking reading progress, the NIP is generic enough to be used in a whole range of other progress tracking scenarios (e.g. Fitness challenges, course progression for learning, personal goals etc..)
nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that includes a minor update to extend kind 30003 in NIP-51 to include the i tag for external identities, as implemented for book reading lists in Open Librarian.
nostr:npub15qydau2hjma6ngxkl2cyar74wzyjshvl65za5k5rl69264ar2exs5cyejr is proposing a NIP that Enable references to commits, files and lines for both nip34 repositories and other git repositories. Useful for code reviews of nip34 patches, the forthcoming nip95 code snippets and referencing specific code more generally.
Notable Projects
Yakihonne nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
🌐web v4.5.0: * Custom reactions are here! Choose your preferred emoji to react to notes and other content. * Improved profile organization with notes and replies now displayed separately. * Adding the ability to zap notes directly from the notifications center. * Enhanced DM filtering by time, allowing you to view only recent messages or browse further back. * Manual cache clearing from settings to optimize web app performance. * Resolved issue preventing users from removing custom media uploader servers. * Expanded export data, including more relevant details in credential and wallet files. * General bug fixes and performance improvements.
📱mobile v1.6.8: * One tap zap: Send a Lightning Network payment with one tap. * Dms extensive filtering: Use advanced filters to sort or prioritise direct messages efficiently. * Separating replies from notes: Split replies and notes in profiles, adding a tab for easier browsing. * Adding slide to display options: Swipe in notifications to access zap, reply, or DM options quickly. * Custom reactions: Choose from a set of emojis for personalised reactions, beyond standard likes. * App cache manager: Manage and clear app cache to boost performance and save space. * Variety of bugs fixed: Fixed multiple bugs for a more stable and seamless app experience. * General app improvements: Enhanced overall performance, usability, and design across the app.
0xchat nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72
0xChat v1.0.2-Desktop Beta is now live! * Supports NIP-104 MLS secret chat. * Copy images directly from the clipboard. * The app stays running after closing the window. * Fixed Enter key sending messages immediately on desktop.
Nostur v1.18.2 nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0
Nostur v1.18.2 bugfix update: * Fixed Follow button sometimes disabled * Fixed account switching reload issue * Fixed custom feeds missing * Fixed live stream banner scroll/swipe issue * Fixed screen turns off while playing video
voca v0.0.6 nostr:npub17h9fn2ny0lycg7kmvxmw6gqdnv2epya9h9excnjw9wvml87nyw8sqy3hpu
This release fine tunes the release process and makes publishing to @Zapstore a lot easier. There are also continuous improvements to initializing the text to speech engine for a faster startup.
WasabiWallet 2.5.0 nostr:npub1jw7scmeuewhywwytqxkxec9jcqf3znw2fsyddcn3948lw9q950ps9y35fg
- 3rd Party Providers for Fee & Exchange Rate
- Quality of Life Features
- Backend and Coordinator packaged for Linux
GitPlaza nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks
- Login via nsec
- Activity feed for the people you follow (only issue creation)
- Create issues
- Comment on issues
ZEUS v0.10.1 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5
ZEUS v0.10.1-beta1 is now available for testing. * NameDesc / bLIP-11 support: add receiver name to invoices * Bug fix: import of QR image from camera roll * Bug fix: Embedded LND: Open Channel: fund max * UI: Add dynamic background/text colors to Android NFC modal
KYCNOT.ME nostr:npub188x98j0r7l2fszeph6j7hj99h8xl07n989pskk5zd69d2fcksetq5mgcqf
- UI/UX - designe a new logo and color palette for kycnot.me.
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services.
- ToS Scrapper: implement a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices.
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services.
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab.
- Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - upgrade the request system. The new form allows you to directly request services or points without any extra steps.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
Long-Form Content Eco
In the past two weeks, more than 569 long-form articles have been published, including over 94 articles on Bitcoin and more than 43 related to Nostr, accounting for 24% of the total content.
These articles about Nostr mainly explore the growing importance of decentralization in communication, identity management, and digital infrastructure. From beginner-friendly guides like Nostr 101 and Getting Started with Primal, to more technical deep dives such as NIP-101e, NIP-95, and tutorials on running Nostr relays as TOR hidden services. Some articles focus on security and privacy—like protecting your Nsec with Amber or using tools such as ProtonMail—while others tackle complex challenges including Sybil attack mitigation and child protection in decentralized environments. There are also cultural and political reflections, such as letters from political prisoners and thoughts on the future of free speech in a post-Twitter world. In addition, the Nostr community shows a strong spirit of experimentation—ranging from agent-to-agent communication through dad jokes, to desktop-like clients, fitness tracking protocols, and Lightning integrations like Work Zaps and Wallet Connect. Together, these pieces showcase a dynamic, resilient, and freedom-driven movement shaping the future of the web.
The Bitcoin articles discuss a wide range of themes—from foundational ideas like "What is Money?" and Bitcoin’s first principles, to practical guides on mining, self-custody, Lightning payments, and privacy tools. Many explore Bitcoin’s role as a hedge against inflation, a form of sovereignty, and a response to fiat fragility. Cultural and economic reflections appear throughout—ranging from using Bitcoin to buy homes in Italy, to hip-hop collaborations, and even personal stories of financial awakening. There's critical analysis of Bitcoin UX, memetics, policy-making, and even war-time monetary history. From node sovereignty to P2P lending, from grassroots adoption to global macro shifts, these articles together portray Bitcoin not just as a currency, but as a cultural movement, a technological evolution, and a lens to reimagine freedom, value, and the future of money.
Thank you, nostr:npub1akzvuyyd79us07m8mtp2ruuha3ylp9757qg46d50rcrkhnx0fs4q2xzr37 nostr:npub1q67f4d7qdja237us384ryeekxsz88lz5kaawrcynwe4hqsnufr6s27up0e nostr:npub1xr8tvnnnr9aqt9vv30vj4vreeq2mk38mlwe7khvhvmzjqlcghh6sr85uum nostr:npub1zmc6qyqdfnllhnzzxr5wpepfpnzcf8q6m3jdveflmgruqvd3qa9sjv7f60 nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 nostr:npub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0 nostr:npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx nostr:npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm nostr:npub186k25a5rymtae6q0dmsh4ksen04706eurfst8xc5uzjchwkxdljqe59hv0 and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.
Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries.
-
YakiHonne teamed up with Bitcoin Safari, nostr:npub1w7z986fez3gmjvxy6dd3sku4ndazhxzafjv2lf6aaa26mtl70q6scz4erj nostr:npub1t4ljwhhg7zlxeahxwgmkwqmn4jjxxq8lzhyuzy0zvy23hq0sacxsdl9fvv nostr:npub1pw778uxwkky3xgq7w3anykdwdw9g46xy8de9mnau0kgwzz375zkq3udv57 and FULAFIA University to successfully host a series of Nostr Workshops, attracting over 200 participants in total. These events introduced the Nostr ecosystem and Bitcoin payments, allowing attendees to explore decentralized technologies through YakiHonne while earning rewards. Participants were encouraged to register and verify their accounts to claim exclusive bonuses—and invite friends to unlock even more benefits.
-
The 2025 Bitcoin, Crypto Economy, and Law FAQ Webinar was held online on March 20, 2025 (Thursday) from 12:00 to 13:00 Argentina time. The webinar was hosted by Martin Paolantonio (Academic Director of the course) and Daniel Rybnik (a lawyer specializing in Banking, Corporate, and Financial Law). The session aimed to introduce the academic program and explored Bitcoin, the crypto economy, and related legal issues.
-
The monthly Bitcoin Meetup organized by Mi Primer Bitcoin took place on Thursday, March 27 at 7:00 PM at CRAFT Basilea in San Salvador. The event featured Bitcoin education, networking opportunities, live music, and fun extras like merchandise, raffles, and more. It was a vibrant evening dedicated to building community and spreading knowledge around Bitcoin. nostr:npub10zuxk4yhygswdmt5n9mfyeq6lh7gcu5g042tlggrgp8yunl32clqsu5t9r
Here is the upcoming Nostr event that you might want to check out.
- Bitcoin Educators Unconference 2025 will take place on April 10, 2025, at Bitcoin Park in Nashville, Tennessee, USA. This event is non-sponsored and follows an Unconference format, allowing all participants to apply as speakers and share their Bitcoin education experiences in a free and interactive environment. the event has open-sourced all its blueprints and Standard Operating Procedures (SOPs) to encourage global communities to organize similar Unconference events.
- Panama Blockchain Week 2025 will take place from April 22 to 24 at the Panama Convention Center in Panama City. As the first large-scale blockchain event in Central America, it aims to position Panama as a leading blockchain financial hub in Latin America. The event features a diverse lineup, including a blockchain conference, Investor’s Night, Web3 gaming experiences, tech exhibitions, and an after-party celebration.
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
 @ dda7ca19:5811f8cd
2025-02-11 12:28:20
@ dda7ca19:5811f8cd
2025-02-11 12:28:20test
-
 @ 10fe3f70:3489c810
2025-04-19 03:28:46
@ 10fe3f70:3489c810
2025-04-19 03:28:46nostr #nostr_writer #review #beginner #obsidian #anytype #contract_drafting #agreenent_drafting #lawyer #law #contract #agreement #learn #education #plugin #telegram #wordpress #yakihonne #primal #damus
How and Why I found Nostr?
I teach contract drafting. That is who I am.
To teach the subject I maintained few websites through self-hosted Wordpress. I faced numerous challenges despite spending money on hosting, domain and whatnot. I do not have any technical background. So, you can understand my frustration when my websites kept disappearing due to hacking. I always put a brave face and started afresh.
I used Microsoft Word, Power Point, and Obsidian to draft my posts and lessons. So, I had some backups. Thankfully, I also did post some of the training sessions on my youtube channel. Checkout my previous post for link to the Youtube Playlist.
Since, I teach for free, every time my websites were hacked, it pained me to see the bad side of human race. I was not hurting anyone, spending my own money, still someone unknown to me, for whatever reasons, could stop my mission.
I started empathising with the belief in the internet being dysfunctional and still being beyond reach of common man.
Then I found some hope, when around a year or so earlier, I found Anytype. A simple app, the everything app, which promises anonymity, security from data breach, and a promise to share ones thoughts publicly with the others soon via web. Although some of its features (e.g. option to self host) are little bit technical for me, I still have high hopes. It is similar to Obsidian, yet way more than that.
I could use either Obsidian or Anytype for writing and publishing my data on web. So, I recently surrendered to the idea of using one of Obsidian's plugins to publish my content. These provide the option to publish your obsidian notes on web through sub-domain. One that I used before was Obsius Plugin.
But, secretly I also wished want more.
I wished to maintain my same anonymous profile I have on Telegram. I have a dedicated student base on Telegram. So, I wanted them to easily find me or atleast my content on a new platform.
I also wanted to stop spending more money, or at least save some by spending less.
And, voila!
I came across Nostr unexpectedly through Obsidian and found a Plugin Nostr Writer by James.
I was looking for a simple method to host my blog posts and lessons on contract drafting. And, I found much more....
If you have some other compelling reasons, as Marc, do read his piece on why he is on Nostr - Why I'm on Nostr?)
What did I find?
After going through the Nostr Writer](https://github.com/jamesmagoo/nostr-writer) documentation on Github, I searched for Nostr and found NOSTR.COM.
As expected, it took me some time to understand the concepts of Public and Private Keys, Clients, Relays and so on. But, within 2-3 days, I found that this was just a SMALL TIP of a HUGE ICEBERG, yet to be show it's full potential.
My most sincere thank you to its creator, and to people who spend time explaining it and making it AWESOME.
NOSTR's CONCEPTS
If you want to READ ABOUT NOSTR's CONCEPTS, you can go through the following:
I also went through almost each and every youtube video I could find on Nostr onboarding and much more. Although, these are very few, I found each one of them to be very useful. I have listed some of these below.
Nostr Onboarding videos
My most sincere thank you to each of the creators (), who took time to explain the onabording by various methods.
- By Ares - how to get started with Nostr on mobile - 3 minutes approx
- By Castig- How to get started on Nostr - 7 minutes approx
- By Max Demarco- Create your Nostr Account- Beginnner Tutorial - 18 minutes approx
- By Nostr World - Nostr for Beginners w/ Derek Ross - 37 minutes approx
- By 88 Sats Radio- how to get started on Nostr - 48 minutes approx
I suggest every beginner must watch all of these videos, create as many accounts you need, and do it until you understand the whole Idea.
This is just the beginning of what to come. So, do not stop using Nostr. In fact refer to friends and family and ask them to join.
Bonus of Nostr
You can get paid in Bitcoins! Without spending a dime!!
Yes, you read it correct.
All you need to do is have a lighting wallet.
I leave it to you explore for now. I am still reviewing the payment structure. So, I will write about how to use this feature later.
Meanwhile I suggest, you go through BTC Session's Youtube channel to learn more about bitcoins, wallets, zaps/sats, lighting, etc.
What else do you need?
Pretty much you have the basics if you did everything suggested above.
If you have a question, you can ask someone within any of the Nostr Clients.
NOSTR CLIENTS
I am experimenting with following Nostr Clients (apps to read your notes, pictures, and long form content) on my apple devices on web.
Damus Primal Yakihonne
NOSTR APPSTORE
You can find many more clients at
GetAlby's App Store Nostr App Store 1 Nostr App Store 2
So, Good luck to you and Happy Nostring
Only the Human Imagination is the limit of what you can do with Nostr
If you liked this article, share it with your friends.
-
 @ 502ab02a:a2860397
2025-04-19 02:39:23
@ 502ab02a:a2860397
2025-04-19 02:39:23เพื่อนๆอาจรู้สึกว่าโพสที่เล่าเรื่อง Precision Fermentation มันดูห่างไกลเหลือเกิน และอาจคิดว่า ณ ตอนนี้ยังสามารถเลือกได้ ไม่เห็นต้องตื่นตูมเลยแค่กินของธรรมชาติก็รอดแล้ว 55555 ไม่เป็นไรครับผมเข้าใจเพราะมันดูไกลตัว และซีรีส์นี้ผมมีเหตุผลในการเขียนอย่างต่อเนื่อง และค้น ค้น ค้น อย่างหนักเพื่อบันทึกการค้นคว้าของผมเอาไว้ ที่ใดสักที่หนึ่ง แล้ววันนึงถึงเวลา จะมีคนค้นดูบ้างว่า โลกมันเกิดอะไรแบบนี้ขึ้นได้ยังไงนะ (ในวงเล็บฮา)
ผมตั้งชื่อตอนนี้ว่า นมที่ไม่มีวัวเกิดขึ้นแล้ว เมื่อ "Perfect Day" พยายามกำหนดอนาคตอาหารให้มนุษย์ทั้งโลกใหม่
ในวันที่โลกกำลังสับสนระหว่างคำว่า “ยั่งยืน” กับ “ควบคุมได้” มีบริษัทหนึ่งที่กำลังสร้างฝันแบบใหม่ให้กับอาหารที่เรากินกันทุกวัน นั่นคือ Perfect Day บริษัทเทคโนโลยีชีวภาพจากสหรัฐฯ ที่ไม่ได้ขายนม แต่มาขายอนาคตว่า “คุณไม่ต้องเลี้ยงวัวอีกต่อไป แต่ยังได้นมที่เหมือนเดิมเป๊ะ” โดยใช้กระบวนการที่เรียกว่า Precision Fermentation นั่นเอง
ฟังดูดีใช่ไหม? แต่ลองก้มดูข้างกล่องอีกที แล้วถามตัวเองว่า “นี่มันอาหาร... หรือผลิตภัณฑ์ทดลองทางพันธุกรรมที่กำลังรุกคืบสู่ชีวิตเราแบบแนบเนียน?”
Perfect Day ผลิตอะไร? Perfect Day ใช้จุลินทรีย์ที่ถูก “ตัดต่อพันธุกรรม” เรียกว่า Microflora ให้สามารถสร้างเวย์โปรตีน (โปรตีนหลักในนม) ได้ในห้องแล็บ มาเลี้ยงในถังหมัก เพื่อผลิตเวย์โปรตีนที่มีโครงสร้างเหมือนกับเวย์จากนมวัวทุกประการ แต่ไม่ต้องใช้สัตว์เลยแม้แต่น้อย แล้วนำโปรตีนนั้นไปใช้ในผลิตภัณฑ์หลากหลาย ตั้งแต่นม ไอศกรีม ไปจนถึงเครื่องดื่มโปรตีน แถมยังชูจุดขายด้วยว่า กระบวนการนี้ช่วยลดการปล่อยก๊าซเรือนกระจกได้ถึง 97% และลดการใช้น้ำได้ถึง 99% เมื่อเทียบกับการผลิตนมแบบดั้งเดิม
ที่สำคัญคือสินค้าจาก Perfect Day มีจำหน่ายแล้วในทุกวันนี้ครับ ในสารพัดแบรนด์เช่น Very Dairy วางขายในสิงคโปร์ Strive FREEMILK ที่ Amazon และร้านค้าในอเมริกา Breyers Lactose-Free Chocolate Ice Cream ร่วมกับ Unilever Modern Kitchen Cream Cheese ที่เคยวางขาย และกำลังปรับกลยุทธ์ และยังมีอีกเพียบเลยครับ
นี่ไม่ใช่ทางเลือก แต่มันคือ “การรุกคืบ” Perfect Day ไม่ได้หยุดแค่ขายของ พวกเขา ขายความคิดว่าของที่พวกเขาผลิต “ดีต่อโลกกว่า” และ “เป็นนวัตกรรมที่จำเป็นต่ออนาคต” โดยที่ไม่พูดถึงว่า -มันถูกสร้างขึ้นจากสิ่งมีชีวิตตัดต่อพันธุกรรม -ต้องใช้เทคโนโลยีสูงที่ประชาชนไม่มีสิทธิผลิตเอง -อยู่ภายใต้สิทธิบัตรที่สามารถควบคุมการใช้วัตถุดิบอาหารได้แต่ผู้เดียว
ลองนึกภาพว่า… วันหนึ่งหากผู้คนคุ้นเคยกับ “นมที่ไม่มีวัว” เพราะมันรสชาติถูกปากถูกใจ แถมยังถูกจริตการรักษ์โลกแบบที่เขาบอกว่าต้องรักอย่างไร และถ้าบริษัทเหล่านี้เข้าถึงโรงเรียน โรงพยาบาล หรือโครงการรัฐ เราจะเหลือ อำนาจในการเลือก จริง ๆ หรือไม่?
เบื้องหลังแผนจากแล็บสู่กลยุทธ์ครอบคลุมตลาด ปี 2023 Perfect Day ขายแบรนด์ฝั่งผู้บริโภคของตน (เช่น The Urgent Company) ให้กับ Superlatus เพื่อโฟกัสเฉพาะ B2B (Business to Business) กลยุทธ์นี้คือการ “เป็นเจ้าของวัตถุดิบ” และปล่อยให้แบรนด์ต่าง ๆ ในตลาดมาเป็นลูกค้า แปลว่าในอนาคต นม ไอศกรีม หรือโปรตีนบาร์ที่คุณกินในทุกวันนี้อาจใช้เวย์โปรตีนจาก GMO โดยที่คุณไม่รู้ตัวก็ได้ จุดนี้หละครับสำคัญ วันไหนนะที่จะมาถึงบ้านเรา
การเข้ายึดครองตลาดไม่ต้องใช้ชื่อ Perfect Day ก็ได้... แค่ฝังมันไว้ในวัตถุดิบ แล้วส่งออกไปยังโรงงานอุตสาหกรรมอาหารทั้งโลก ควบคุมอยู่เบื้องหลังเป็นกระดูกสันหลังที่สำคัญต่อการเคลื่อนที่ไปโดยปริยาย
ทั้งนี้เพราะ Perfect Day มีพันธมิตรมากมาย ไม่ว่าจะเป็น Unilever / Nestlé / Mars / Bel Group / Coolhaus / Very Dairy / Ice Age! / Strive Nutrition และอื่นๆอีกมากมาย
ที่น่าสนใจคือ มีหลักฐานชัดเจนว่า Nestlé ได้ร่วมมือกับ Perfect Day ในการพัฒนาผลิตภัณฑ์นมที่ปราศจากสัตว์ โดยใช้เวย์โปรตีนที่ผลิตจากกระบวนการ precision fermentation ของ Perfect Day
ความร่วมมือระหว่าง Nestlé และ Perfect Day เกิดขึ้นในเดือนกันยายน 2022 โดย Nestlé ได้ประกาศความร่วมมือกับ Perfect Day เพื่อพัฒนาผลิตภัณฑ์นมที่ปราศจากสัตว์ โดยใช้เวย์โปรตีนที่ผลิตจากจุลินทรีย์ที่ได้รับการดัดแปลงพันธุกรรม ผลิตภัณฑ์ที่พัฒนาขึ้น ได้แก่ เครื่องดื่มนมพร้อมดื่ม (RTD) รสช็อกโกแลตและรสดั้งเดิม ภายใต้ชื่อแบรนด์ Cowabunga ซึ่งวางจำหน่ายในร้าน Safeway บางแห่งในแคลิฟอร์เนีย Green Queen ความร่วมมือนี้เป็นส่วนหนึ่งของโครงการ R+D Accelerator ของ Nestlé ในสหรัฐอเมริกา ซึ่งมุ่งเน้นการพัฒนาและทดสอบผลิตภัณฑ์ใหม่ๆ อย่างรวดเร็ว
Nestlé ได้ร่วมมือกับ Perfect Day ในการพัฒนาผลิตภัณฑ์นมที่ปราศจากสัตว์ โดยใช้เวย์โปรตีนที่ผลิตจากกระบวนการ precision fermentation ซึ่งเป็นการตอบสนองต่อความต้องการของผู้บริโภคที่มองหาทางเลือกที่ยั่งยืนและเป็นมิตรต่อสิ่งแวดล้อม
ณ เดือนมกราคม 2025 บริษัท Perfect Day มีรายได้ประจำปีในปี 2024 Perfect Day มีรายได้รวมประมาณ 35 ล้านดอลลาร์สหรัฐ มูลค่าบริษัทจากการระดมทุนรอบล่าสุดในเดือนมกราคม 2024 ทำให้บริษัทมีมูลค่าประเมินอยู่ที่ 1.6 พันล้านดอลลาร์สหรัฐ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ e968e50b:db2a803a
2025-04-15 13:47:13
@ e968e50b:db2a803a
2025-04-15 13:47:13There's really not much to say. I just wanted to put a bug in the ear of anybody else that has to deal with water problems and has a few old, unprofitable s9s sitting around. At least you'll get your KYC-free bitcoin rebate. Is there a business opportunity here?!?
originally posted at https://stacker.news/items/944025
-
 @ fd06f542:8d6d54cd
2025-04-19 01:32:25
@ fd06f542:8d6d54cd
2025-04-19 01:32:25直车对横车 的概念
顺炮直车对横车:红方出直车(车一平二),黑方出横车(车 9 进 1),这是顺炮布局中常见的一种变化。红方直车可以快速出动,威胁黑方右翼,黑方横车则可以灵活调动,根据局势选择进攻或防守的方向。后续可能会出现红方进车过河压马,黑方出炮封车等变化,双方展开激烈的争夺。
顺炮直车对横车布局体系主要有以下分类:
- 古典攻法
- 顺炮过河车对横车:红车一平二后车二进六过河,以强硬攻势迅速压制黑方阵营。
- 顺炮缓补士对横车:红出直车后不急于补士(士四进五缓出) ,依黑方行棋灵活选择攻防策略。
- 顺炮跳边马对横车:红马八进九上边马,平炮通车平衡两翼子力,防止黑卒3进1争先,着法稳健。
- “胡氏双正马”攻法
- 顺炮直车进三兵对横车挺3卒:红进三兵、黑挺3卒形成牵制,红可借马三进四等手段跃马进攻。
- 顺炮直车进三兵对横车跳边马:红进三兵后,针对黑边马位置,以炮八平七等手段威胁黑方马获取局面优势。
- 顺炮直车进七兵对横车:红进七兵,黑车9平4后,红可选择车二进四巡河或车二进六过河等不同进攻战术。
- 顺炮直车“两头蛇”对双横车:红兵三进一、兵七进一构成“两头蛇”阵,与黑方双横车激烈争夺,红借双兵推进掌控空间,黑寻机反击。
- 其他常见变化
- 正马三兵与黑右肋车的攻防对抗;正马应对黑挺3卒的局面变化。
- 正马三兵对阵黑肋车边马;“两头蛇”阵势迎战黑双横车的局势博弈。
- 正马三兵对黑方马后藏车;“两头蛇”对黑正马边炮的局势发展。
- 红方正马左士应对黑右肋车;红方采用巡河车、五六炮的布局变化,以及双正马进七兵分别对黑正马、右肋车的局面策略 。
以下按照天天象棋棋谱整理的8种变化,这些变化有些大同小异。 最后都类似。
车二进六的变化(82)
双正马三兵 变化(2202)
兵三进一 (473)
马八进九 (179)
红正马五六炮式(171)
兵七进一 (74)
红正马巡河车式(73)
士四进五(55)
- 古典攻法
-
 @ d08c9312:73efcc9f
2025-04-18 20:17:41
@ d08c9312:73efcc9f
2025-04-18 20:17:41https://youtu.be/qK7ffYzxiiQ
Resolvr was recently featured in The Institutes RiskStream Collaborative's educational video series on insurance digitization and cross-border payments. With over a century of history educating insurance professionals, The Institutes has established itself as the premier knowledge resource in risk management and insurance. And its RiskStream Collaborative non-profit serves as the industry's largest enterprise-level technology consortium focused on streamlining insurance processes through innovative solutions.
Resolvr's co-founders, Aaron Daniel and Dave Schwab, were joined by industry experts Lizzy Eisenberg from Lightspark and Austin Cornell from Zero Hash to discuss how Bitcoin and the Lightning Network are transforming global insurance payments operations.
Watch the video to learn how Resolvr is leveraging these real-time digital settlement networks to solve significant inefficiencies in today's insurance payment ecosystem - from the months-long settlement times that trap billions in value, to the manual reconciliation processes costing the industry nearly £1 billion annually at Lloyd's of London alone.
We're grateful to RiskStream Collaborative for showcasing these transformative technologies and emphasizing the importance of combining specialized insurance-native interfaces with powerful payment infrastructure to solve industry-specific challenges.
For more information about how Resolvr can help your organization streamline premium processing and payments, contact us today.
-
 @ d5c3d063:4d1159b3
2025-04-01 04:20:50
@ d5c3d063:4d1159b3
2025-04-01 04:20:50“วิธีที่ดีที่สุดในการทำลายทุนนิยมคือทำลายค่าเงิน” Lenin Was Right
ประโยคนี้ไม่ใช่แค่คำปลุกระดมของนักปฏิวัติ แต่มันเป็นเหมือนสัญญาณเตือนล่วงหน้า ที่คนส่วนใหญ่ไม่สนใจ จนวันหนึ่งมันก็เกิดขึ้นจริง แบบเงียบ ๆ โดยไม่มีใครทันตั้งตัว
Henry Hazlitt เขียนบทความนี้ไว้ตั้งแต่ปี 1947 เขาไม่เพียงบอกว่าเลนินพูดถูก แต่เขาแฉว่าโลกทั้งใบ “กำลังทำตามแผนของเลนิน” แบบไม่รู้ตัว
ตอนนั้นรัฐบาลหลายประเทศ โดยเฉพาะในยุโรป พิมพ์เงินออกมาใช้มหาศาล โดยอ้างว่าสงครามบีบบังคับให้ต้องทำแบบนั้น แต่ปัญหาคือ...พอสงครามจบในปี 1945 แล้ว รัฐกลับไม่หยุดพิมพ์เงิน ยังทำเหมือนอยู่ในภาวะฉุกเฉิน
เหมือนที่ อ. #SaifedeanAmmous พูดไว้ในหนังสือ #TheBitcoinStandard ว่าเวลารัฐอยากพิมพ์เงินแบบไม่ต้องรับผิดชอบ ก็แค่เอาสงครามมาอ้าง พอพูดว่า “เพื่อความมั่นคง” หรือ “เพื่อชาติ” เท่านั้นแหละ ทุกอย่างก็ดูเป็นเรื่องจำเป็นขึ้นมาทันที แล้วไม่มีใครกล้าถามว่าจริง ๆ แล้วเงินมันมาจากไหน
พอเงินเฟ้อมันแรง ของก็แพงขึ้น แต่รัฐไม่ยอมรับหรอกว่าที่ของแพงเพราะตัวเองพิมพ์เงินออกมาเยอะเกิน แต่กลับไปโทษพ่อค้า โทษคนทำธุรกิจ ว่าขายของแพง ค้ากำไรเกินควรซะงั้น
Hazlitt เขาเตือนว่า...รัฐกำลังทำให้คนเกลียดพ่อค้า เกลียดเจ้าของธุรกิจ เพื่อให้ดูเหมือนว่าตัวเองมีเหตุผลที่จะเข้ามาคุมเศรษฐกิจ ซึ่งที่น่ากลัวคือ... มันไม่ได้เกิดจากความไม่รู้ แต่มันเกิดจาก “ระบบ” ที่เปิดช่องให้เขาทำแบบนี้ได้เลย แบบไม่ต้องรับผิดชอบอะไรทั้งนั้น
ตรงนี้แหละที่ Hazlitt เอาคำพูดของ John Maynard Keynes เข้ามาเสริม เพราะแม้แต่ Keynes ก็ยังเคยเตือนไว้ในหนังสือ The Economic Consequences of the Peace ว่า “เงินเฟ้อ” มันเหมือนเครื่องมือเงียบ ๆ ที่จะค่อย ๆ ทำลายระบบเศรษฐกิจ โดยที่คนส่วนใหญ่ไม่รู้ตัว
Hazlitt เขาเป็น "สายวิจารณ์" Keynes ตัวพ่อเลยนะ เขาเขียนหนังสือ The Failure of the New Economics ที่ไล่รื้อแนวคิดของ Keynes แบบ “ตา-ต่อ-ตา หน้า-ต่อ-หน้า” กับหนังสือ The General Theory ของ Keynes เลยนะ
แต่พอมาในบทความนี้...Hazlitt กลับหยิบคำพูดของ Keynes มาใช้อย่างเต็มใจ เพราะมันตรงเกินไปที่จะมองข้ามได้ ว่าแม้แต่ #Keynes เองยังเคยเตือนเลยว่า “การทำลายค่าเงิน” คืออาวุธเงียบ ที่ใช้ทำลายระบบทุนนิยมได้อย่างแนบเนียนที่สุด . . พออ่านแล้วแบบ…แม้แต่คนที่เราคิดว่าเชียร์ฝั่งรัฐ ยังเตือนเรื่องนี้ไว้ แล้วเราจะยังเฉยอยู่ได้ไง
คือถ้าเงินมันถูกทำให้ด้อยค่าลงเรื่อย ๆ วันนึงมันจะพังแบบเงียบ ๆ จนคนไม่รู้ตัวเลย คนทั่วไปจะรู้แค่ว่าของมันแพงขึ้น แต่ไม่มีใครเห็น ว่าจริง ๆ แล้ว เงินที่เราใช้มันเริ่มไม่มีเสถียรภาพ และไม่มั่นคงอีกต่อไปแล้ว
แล้วถ้ามองตัวเลขนี่ยิ่งช็อก ระหว่างปี 1939 ถึง 1947 ในเวลาแค่ 8 ปี ปริมาณเงินในระบบของสหรัฐฯ เพิ่มจาก 33,000 ล้านดอลลารเป็น 108,500 ล้านดอลลาร์ พูดง่าย ๆ คือ คูณสาม (ช่วงสงครามโลกครั้งที่ 2)
Hazlitt พูดแบบตรง ๆ เลยว่า ปัญหาที่เกิดขึ้น มันไม่ใช่เพราะเศรษฐกิจโตหรือคนรวยขึ้นนะ มันเกิดจากการที่รัฐเพิ่มปริมาณเงินในระบบเร็วเกินไป เมื่อเงินในตลาดเลยเยอะขึ้น แต่ของที่มีให้ซื้อไม่ได้เยอะขึ้นตาม เมื่อเงินไหลเวียนมากขึ้น โดยที่ของยังมีเท่าเดิม ราคาของก็เลยพุ่ง
ทีนี้พอของขึ้นราคา รัฐบาลกลับไม่ยอมรับว่าเป็นเพราะเขาพิมพ์เงิน แต่ไปเลือกวิธีแก้แบบง่าย ๆ แต่สร้างปัญหาในระยะยาว เช่น สั่งห้ามขึ้นราคา กดดันคนทำธุรกิจให้แบกต้นทุนไว้ หรือไม่ก็ล็อกค่าเงิน เหมือนไม่มีอะไรเกิดขึ้น
หลังจากนั้น เศรษฐกิจยุโรปก็เริ่มพัง ผู้ผลิตเจอต้นทุนบาน การค้าระหว่างประเทศก็รวน สุดท้ายก็ต้องพึ่งดอลลาร์จากอเมริกา (Marshall Aid) มาช่วยอุ้ม เหมือนพิมพ์เงินของตัวเองจนระบบรวน แล้วไปขอเงินจากฝั่งที่พิมพ์ได้มากกว่าอีกที
นี่แหละจุดเริ่มของ “วิกฤตเศรษฐกิจโลกหลังสงคราม” ที่จริง ๆ แล้ว...ก็แค่เรื่องของการพิมพ์เงินล้วน ๆ . . แต่นั้นมันเป็นเรื่องเกิดขึ้นเมื่อปี 1947 นะ...แล้ววันนี้ล่ะ
ล่าสุด ปี 2020 ก่อนโควิด ระดับ M2 money supply ของสหรัฐอยู่ราว ๆ 15 ล้านล้านดอลลาร์ แค่ไม่กี่ปีต่อมา มันทะลุไปถึง 21 ล้านล้าน ในเวลาไม่ถึง 3 ปีเงินเพิ่มขึ้นในระบบเศรษฐกิจกว่า 6 ล้านล้านดอลลาร์
แล้วของก็แพงขึ้น ค่าแรงวิ่งตามไม่ทัน แต่แทนที่รัฐจะบอกว่า “เราพิมพ์เงินมากไป” ก็ไปเล่นมุกเดิม โทษตลาด โทษนายทุน โทษธุรกิจ (บ้างก็โทษโลกร้อน)
สุดท้ายก็จะมีคนบางกลุ่มเชียร์ให้ “ควบคุมราคา” อีก มันคือ loop เดิม ที่ #Hazlitt เคยเตือนไว้ เมื่อเกือบ 80 ปีก่อน.. . . สิ่งที่ซุปเห็นชัดเจนที่สุดจากบทความนี้คือ... เกมนี้มันไม่มีใครหยุดได้เลย ถ้าคุณยังถือเงินที่รัฐพิมพ์ได้
เพราะตราบใดที่ยังมีคนสั่งพิมพ์เงินได้ตามใจ ระบบเศรษฐกิจก็จะปั่นป่วนซ้ำไปซ้ำมา ของก็จะแพงขึ้นเรื่อย ๆ แบบไม่มีจุดจบ
คุณก็จะต้องเหนื่อยทำงานมากขึ้น แต่ซื้อได้น้อยลง แล้วคุณก็จะโทษตัวเอง ว่ายังขยันไม่มากพอ ทั้ง ๆ ที่คุณทำงาน 4-5 อย่าง
.
เลนิน พูดถูก ถ้าจะทำลายทุนนิยม ก็แค่ทำลายค่าเงิน ฟังดูแรงเนอะ...แต่เรื่องนี้มันไม่ใช่แค่ทฤษฎีแล้ว เพราะเรากำลังเห็น ว่ามันกำลังเกิดขึ้นอยู่จริง ๆ
แต่วันนี้ เราเลือกที่จะไม่อยู่ในเกมที่พังซ้ำๆ ได้แล้ว
เพราะเรามี “ทางออก” อยู่ตรงหน้า บิตคอยน์ ไม่ใช่อะไรที่ทุกคนจะเข้าใจมันได้ทันที แต่มันคือ “เงิน” ที่ไม่มีใครพิมพ์เพิ่มได้ตามใจ ไม่มีใครมานั่งกดปุ่มสร้างมันขึ้นมาได้ง่าย ๆ ไม่มีใครเปลี่ยนกติกากลางเกมได้ และไม่มีใครแทรกแซงนโยบายของมันได้
สิ่งเดียวที่ #บิตคอยน์ บอกเราตรง ๆ ก็คือ “ความขาดแคลน” ไม่ใช่ปัญหา...
สิ่งที่ Hazlitt เตือนเมื่ออดีต คือกับดักของเงินไม่มีขอบเขต
สิ่งที่ #Bitcoin เสนอ คือขอบเขตที่ทำให้ “มูลค่า” กลับมามีความหมาย
[Newsweek column from September 22, 1947, and reprinted in Business Tides: The Newsweek Era of Henry Hazlitt.] https://mises.org/mises-wire/lenin-was-right
Siamstr
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 266815e0:6cd408a5
2025-04-15 06:58:14
@ 266815e0:6cd408a5
2025-04-15 06:58:14Its been a little over a year since NIP-90 was written and merged into the nips repo and its been a communication mess.
Every DVM implementation expects the inputs in slightly different formats, returns the results in mostly the same format and there are very few DVM actually running.
NIP-90 is overloaded
Why does a request for text translation and creating bitcoin OP_RETURNs share the same input
itag? and why is there anoutputtag on requests when only one of them will return an output?Each DVM request kind is for requesting completely different types of compute with diffrent input and output requirements, but they are all using the same spec that has 4 different types of inputs (
text,url,event,job) and an undefined number ofoutputtypes.Let me show a few random DVM requests and responses I found on
wss://relay.damus.ioto demonstrate what I mean:This is a request to translate an event to English
json { "kind": 5002, "content": "", "tags": [ // NIP-90 says there can be multiple inputs, so how would a DVM handle translatting multiple events at once? [ "i", "<event-id>", "event" ], [ "param", "language", "en" ], // What other type of output would text translations be? image/jpeg? [ "output", "text/plain" ], // Do we really need to define relays? cant the DVM respond on the relays it saw the request on? [ "relays", "wss://relay.unknown.cloud/", "wss://nos.lol/" ] ] }This is a request to generate text using an LLM model
json { "kind": 5050, // Why is the content empty? wouldn't it be better to have the prompt in the content? "content": "", "tags": [ // Why use an indexable tag? are we ever going to lookup prompts? // Also the type "prompt" isn't in NIP-90, this should probably be "text" [ "i", "What is the capital of France?", "prompt" ], [ "p", "c4878054cff877f694f5abecf18c7450f4b6fdf59e3e9cb3e6505a93c4577db2" ], [ "relays", "wss://relay.primal.net" ] ] }This is a request for content recommendation
json { "kind": 5300, "content": "", "tags": [ // Its fine ignoring this param, but what if the client actually needs exactly 200 "results" [ "param", "max_results", "200" ], // The spec never mentions requesting content for other users. // If a DVM didn't understand this and responded to this request it would provide bad data [ "param", "user", "b22b06b051fd5232966a9344a634d956c3dc33a7f5ecdcad9ed11ddc4120a7f2" ], [ "relays", "wss://relay.primal.net", ], [ "p", "ceb7e7d688e8a704794d5662acb6f18c2455df7481833dd6c384b65252455a95" ] ] }This is a request to create a OP_RETURN message on bitcoin
json { "kind": 5901, // Again why is the content empty when we are sending human readable text? "content": "", "tags": [ // and again, using an indexable tag on an input that will never need to be looked up ["i", "09/01/24 SEC Chairman on the brink of second ETF approval", "text"] ] }My point isn't that these event schema's aren't understandable but why are they using the same schema? each use-case is different but are they all required to use the same
itag format as input and could support all 4 types of inputs.Lack of libraries
With all these different types of inputs, params, and outputs its verify difficult if not impossible to build libraries for DVMs
If a simple text translation request can have an
eventortextas inputs, apayment-requiredstatus at any point in the flow, partial results, or responses from 10+ DVMs whats the best way to build a translation library for other nostr clients to use?And how do I build a DVM framework for the server side that can handle multiple inputs of all four types (
url,text,event,job) and clients are sending all the requests in slightly differently.Supporting payments is impossible
The way NIP-90 is written there isn't much details about payments. only a
payment-requiredstatus and a genericamounttagBut the way things are now every DVM is implementing payments differently. some send a bolt11 invoice, some expect the client to NIP-57 zap the request event (or maybe the status event), and some even ask for a subscription. and we haven't even started implementing NIP-61 nut zaps or cashu A few are even formatting the
amountnumber wrong or denominating it in sats and not mili-satsBuilding a client or a library that can understand and handle all of these payment methods is very difficult. for the DVM server side its worse. A DVM server presumably needs to support all 4+ types of payments if they want to get the most sats for their services and support the most clients.
All of this is made even more complicated by the fact that a DVM can ask for payment at any point during the job process. this makes sense for some types of compute, but for others like translations or user recommendation / search it just makes things even more complicated.
For example, If a client wanted to implement a timeline page that showed the notes of all the pubkeys on a recommended list. what would they do when the selected DVM asks for payment at the start of the job? or at the end? or worse, only provides half the pubkeys and asks for payment for the other half. building a UI that could handle even just two of these possibilities is complicated.
NIP-89 is being abused
NIP-89 is "Recommended Application Handlers" and the way its describe in the nips repo is
a way to discover applications that can handle unknown event-kinds
Not "a way to discover everything"
If I wanted to build an application discovery app to show all the apps that your contacts use and let you discover new apps then it would have to filter out ALL the DVM advertisement events. and that's not just for making requests from relays
If the app shows the user their list of "recommended applications" then it either has to understand that everything in the 5xxx kind range is a DVM and to show that is its own category or show a bunch of unknown "favorites" in the list which might be confusing for the user.
In conclusion
My point in writing this article isn't that the DVMs implementations so far don't work, but that they will never work well because the spec is too broad. even with only a few DVMs running we have already lost interoperability.
I don't want to be completely negative though because some things have worked. the "DVM feeds" work, although they are limited to a single page of results. text / event translations also work well and kind
5970Event PoW delegation could be cool. but if we want interoperability, we are going to need to change a few things with NIP-90I don't think we can (or should) abandon NIP-90 entirely but it would be good to break it up into small NIPs or specs. break each "kind" of DVM request out into its own spec with its own definitions for expected inputs, outputs and flow.
Then if we have simple, clean definitions for each kind of compute we want to distribute. we might actually see markets and services being built and used.
-
 @ 0fa80bd3:ea7325de
2025-01-30 04:28:30
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30"Degeneration" or "Вырождение" ![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-
 @ 7d33ba57:1b82db35
2025-04-18 19:29:49
@ 7d33ba57:1b82db35
2025-04-18 19:29:49The San Blas Islands, officially known as the Guna Yala archipelago, are a dreamy chain of 365 islands and cays, most of them uninhabited, off Panama’s Caribbean coast. Run autonomously by the Guna (or Kuna) people, San Blas is known for its **crystal-clear turquoise waters, white sand beaches, and authentic indigenous culture.
🌞 Why Visit the San Blas Islands?
- Unspoiled beauty: No resorts or big hotels—just rustic cabanas, palm trees, and silence
- Snorkeling heaven: Coral reefs, starfish banks, and calm lagoons await
- Cultural connection: Meet the Guna people, learn about their traditions, and buy their handmade molas (textiles)
- Disconnect to reconnect: No Wi-Fi, no distractions—just sea, sky, and sand
🌊 Top Things to Do
- 🐠 Snorkel around the vibrant reefs and shipwrecks
- 🏝️ Island-hop by boat between tiny islets, some with just a few palm trees
- 🧺 Visit a Guna village to learn about their matriarchal society and way of life
- 🌅 Sunbathe or hammock-nap under swaying palms
- 🌌 Gaze at star-filled skies—zero light pollution here
🛏️ Where to Stay
- Accommodations are basic cabanas or eco-lodges, often directly on the beach
- Meals (mostly fresh seafood, rice, plantains) are usually included
- Power is limited—think solar lights, not outlets
🚐 Getting There
- Depart from Panama City via a 4x4 ride (2.5–3 hrs) to the port of Cartí
- Then hop on a boat (30–45 mins) to your island
- Or opt for a guided multi-day tour that includes transport, meals, and accommodation
🛂 Note: San Blas is semi-autonomous—you’ll need your passport for entry, even if coming from within Panama.
📅 Best Time to Go
- Dry Season (Dec–April): Clear skies, calm seas, and stunning sunrises
- Wet Season (May–Nov): Still beautiful, with occasional short tropical showers
🌺 Insider Tips
- Bring cash—no ATMs in San Blas
- Pack reef-safe sunscreen, a dry bag, and snorkeling gear
- Respect Guna customs—ask before taking photos, and dress modestly when visiting villages
- Travel light—waterproof bags are a must for boat rides
-
 @ 6be5cc06:5259daf0
2025-01-21 23:17:29
@ 6be5cc06:5259daf0
2025-01-21 23:17:29A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ b17fccdf:b7211155
2025-01-21 17:02:21
@ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor introduced officially a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks.
~ > This feature at the moment, is deactivate by default, so you need to follow these steps to activate this on a MiniBolt node:
- Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing
tor --versionExample of expected output:
Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0~ > If you have v0.4.8.X, you are OK, if not, type
sudo apt update && sudo apt upgradeand confirm to update.- Basic PoW support can be checked by running this command:
tor --list-modulesExpected output:
relay: yes dirauth: yes dircache: yes pow: **yes**~ > If you have
pow: yes, you are OK- Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added
sudo nano /etc/tor/torrcExample:
```
Hidden Service BTC RPC Explorer
HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ```
~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links:
- Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002
- LND: https://github.com/bitcoin/bitcoin/issues/28499
More info:
- https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/
- https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ
Enjoy it MiniBolter! 💙
-
 @ f3328521:a00ee32a
2025-03-31 00:25:36
@ f3328521:a00ee32a
2025-03-31 00:25:36This paper was originaly writen in early November 2024 as a proposal for an international Muslim entrepreneurial initiative. It was first publish on NOSTR 27 November 2024 as part 1 of a 4 part series of essays. Last updated/revised: 30 March 2025.
The lament of the Ummah for the past century has been the downfall of the Khalifate. With the genocide in occupied Palestine over the past year and now escalations in Lebanon as well, this concern is at the forefront of a Muslim’s mind. In our tradition, when one part of the Ummah suffers, all believers are affected and share in that suffering. The Ummah today has minimal sovereignty at best. It lacks a Khalifate. It is spiritually weakened due to those not practicing and fulfilling their duties and responsibilities. And, as we will address in this paper, it has no real economic power. In our current monetary system, it is nearly impossible to avoid the malevolence of riba (interest) – one of the worst sins. However, with bitcoin there is an opportunity to alleviate this collective suffering and reclaim economic sovereignty.
Since it’s invention 15 years ago, bitcoin has risen to achieve a top 10 market cap ranking as a global asset (currently valued at $1.8 trillion USD). Institutional investors are moving full swing to embrace bitcoin in their portfolios. Recent proposals in Kazan hint that BRICS may even be utilizing bitcoin as part of their new payments system. State actors will be joining soon. With only about 1 million bitcoins left to be mined we need to aim to get as much of those remaining coins as possible into the wallets of Muslims over the next decade. Now is the time to onboard the Ummah. This paper presents Bitcoin as the best option for future economic sovereignty of the Ummah and proposes steps needed to generate a collective waqf of an initial 0.1%-0.5% chain dominance to safeguard a revived Khalifate.
Money is the protocol that facilitates economic coordination to help the development and advancement of civilization. Throughout history money has existed as cattle, seashells, salt, beads, stones, precious metals. Money develops naturally and spontaneously; it is not the invention of the state (although it at times is legislated by states). Money exists marginally, not by fiat. During the past few millenniums, gold and silver were optimally used by most advanced civilizations due to strong properties such as divisibility, durability, fungibility, portability, scarcity, and verifiability. Paper money modernized usability through attempts to enhance portability, divisibility, and verifiability. However, all these monetary properties are digitized today. And with the increase of fractional-reserve banking over the past two centuries, riba is now the de facto foundation of the consensus reserve currency – the USD.
This reserve currency itself is backed by the central banking organ of the treasury bond markets which are essentially government issued debt. Treasurey bonds opperate by manipulating the money supply arbitrarily with the purpose of targeting a set interest rate – injecting or liquidating money into the supply by fiat to control intrest yeilds. At its root, the current global monetary order depends entirely on riba to work. One need not list the terrible results of riba as Muslims know well its harshness. As Lyn Alden wonderful states in her book, Broken Money, “Everything is a claim of a claim of a claim, reliant on perpetual motion and continual growth to not collapse”. Eventual collapse is inevitable, and Muslims need to be aware and prepared for this reality.
The status quo among Muslims has been to search for “shariah compliance”. However, fatwa regarding compliance as well as the current Islamic Banking scene still operate under the same fiat protocol which make them involved in the creation of money through riba. Obfuscation of this riba through contractum trinius or "shariah compliant" yields (which are benchmarked to interest rates) is simply an attempt to replicate conventional banking, just with a “halal” label. Fortunately, with the advent of the digital age we now have other monetary options available.
Experiments and theories with digital money date back to the 1980s. In the 1990s we saw the dot com era with the coming online of the current fiat system, and in 2008 Satoshi Nakamoto released Bitcoin to the world. We have been in the crypto era ever since. Without diving into the technical aspects of Bitcoin, it is simply a P2P e-cash that is cryptographically stored in digital wallets and secured via a decentralized blockchain ledger. For Muslims, it is essential to grasp that Bitcoin is a new type of money (not just an investment vehicle or payment application) that possesses “anti-riba” properties.
Bitcoin has a fixed supply cap of 21 million, meaning there will only ever be 21 million Bitcoin (BTC). Anyone with a cheap laptop or computer with an internet connection can participate on the Bitcoin network to verify this supply cap. This may seem like an inadequate supply for global adoption, but each bitcoin is highly divisible into smaller units (1 btc = 100,000,000 satoshis or sats). Bitcoins are created (or mined) from the processing of transactions on the blockchain which involves expending energy in the real world (via CPU power) and providing proof that this work was done.
In contrast, with the riba-based fiat system, central banks need to issue debt instruments, either in the form of buying treasuries or through issuing a bond. Individual banks are supposed to be irresponsibly leveraged and are rewarded for making risky loans. With Bitcoin, there is a hard cap of 21 million, and there is no central authority that can change numbers on a database to create more money or manipulate interest rates. Under a Bitcoin standard, money is verifiably stored on a ledger and is not loaned to create more money with interest. Absolute scarcity drives saving rather than spending, but with increasing purchasing power from the exponentially increasing demand also comes the desire to use that power and increased monetary economization. With bitcoin you are your own bank, and bitcoin becomes for your enemies as much as it is for your friends. Bitcoin ultimately provides a clean foundation for a stable money that can be used by muslims and should be the currency for a future Khalifate.
The 2024 American presidential election has perhaps shown more clearly than ever the lack of politcal power that American Muslims have as well as the dire need for them to attain political influence. Political power comes largely through economic sovereignty, military might, and media distribution. Just a quick gloss of Muslim countries and Turkey & Egypt seem to have decent militaries but failing economies. GCC states have good economies but weak militaries. Iran uniquely has survived sanctions for decades and despite this weakened economic status has still been able to make military gains. Although any success from its path is yet to be seen it is important to note that Iran is the only country that has been able to put up any clear resistance to western powers. This is just a noteworthy observation and as this paper is limited to economic issues, full analysis of media and miliary issues must be left for other writings.
It would also be worthy to note that BDS movements (Boycott, Divest & Sanction) in solidarity with Palestine should continue to be championed. Over the past year they have undoubtedly contributed to PEP stock sinking 2.25% and MCD struggling to break even. SBUX and KO on the other hand, despite active boycott campaigns, remain up 3.5% & 10.6% respectively. But some thought must be put into why the focus of these boycotts has been on snack foods that are a luxury item. Should we not instead be focusing attention on advanced tech weaponry? MSFT is up 9.78%, GOOG up 23.5%, AMZN up 30%, and META up 61%! It has been well documented this past year how most of the major tech companies have contracts with occupying entity and are using the current genocide as a testing ground for AI. There is no justification for AI being a good for humanity when it comes at the expense of the lives of our brothers in Palestine. However, most “sharia compliant” investment guides still list these companies among their top recommendations for Muslims to include in their portfolios.
As has already been argued, by investing in fiat-based organization, businesses, ETFs, and mutual funds we are not addressing the root cause of riba. We are either not creating truly halal capital, are abusing the capital that Allah has entrusted to us or are significantly missing blessings that Allah wants to give us in the capital that we have. If we are following the imperative to attempt to make our wealth as “riba-free” as possible, then the first step must be to get off zero bitcoin
Here again, the situation in Palestine becomes a good example. All Palestinians suffer from inflation from using the Israeli Shekel, a fiat currency. Palestinians are limited in ways to receive remittances and are shrouded in sanctions. No CashApp, PayPal, Venmo. Western Union takes huge cuts and sometimes has confiscated funds. Bank wires do this too and here the government sanctions nearly always get in the way. However, Palestinians can use bitcoin which is un-censorable. Israel cannot stop or change the bitcoin protocol. Youssef Mahmoud, a former taxi driver, has been running Bitcoin For Palestine as a way for anyone to make a bitcoin donation in support of children in Gaza. Over 1.6 BTC has been donated so far, an equivalent of about $149,000 USD based on current valuation. This has provided a steady supply of funds for the necessary food, clothing, and medication for those most in need of aid (Note: due to recent updates in Gaza, Bitcoin For Palestine is no longer endorsed by the author of this paper. However, it remains an example of how the Bitcoin network opperates through heavy sanctions and war).
Over in one of the poorest countries in the world, a self-managed orphanage is providing a home to 77 children without the patronage of any charity organization. Orphans Of Uganda receives significant funding through bitcoin donations. In 2023 and 2024 Muslims ran Ramadan campaigns that saw the equivalent of $14,000 USD flow into the orphanage’s bitcoin wallet. This funding enabled them to purchase food, clothing, medical supplies and treatment, school costs, and other necessities. Many who started donating during the 2023 campaign also have continued providing monthly donations which has been crucial for maintaining the well-being of the children.
According to the Muslim Philanthropy Initiative, Muslim Americans give an estimated $1.8 billion in zakat donations every year with the average household donating $2070 anually. Now imagine if international zakat organizations like Launchgood or Islamic Relief enabled the option to donate bitcoin. So much could be saved by using an open, instant, permissionless, and practically feeless way to send zakat or sadaqah all over the world! Most zakat organizations are sleeping on or simply unaware of this revolutionary technology.
Studies by institutions like Fidelity and Yale have shown that adding even a 1% to 5% bitcoin allocation to a traditional 60/40 stock-bond portfolio significantly enhances returns. Over the past decade, a 5% bitcoin allocation in such a portfolio has increased returns by over 3x without a substantial increase in risk or volatility. If American Muslims, who are currently a demographic estimated at 2.5 million, were to only allocate 5% ($270 million) of their annual zakat to bitcoin donations, that would eventually become worth $14.8 billion at the end of a decade. Keep in mind this rate being proposed here is gathered from American Muslim zakat data (a financially privileged population, but one that only accounts for 0.04% of the Ummah) and that it is well established that Muslims donate in sadaqa as well. Even with a more conservative rate of a 1% allocation you would still be looking at nearly $52 million being liquidated out of fiat and into bitcoin annually. However, if the goal is to help Muslims hit at least 0.1% chain dominance in the next decade then a target benchmark of a 3% annual zakat allocation will be necessary.
Islamic financial institutions will be late to the game when it comes to bitcoin adoption. They will likely hesitate for another 2-4 years out of abundance of regulatory caution and the persuasion to be reactive rather than proactive. It is up to us on the margin to lead in this regard. Bitcoin was designed to be peer-2-peer, so a grassroots Muslim bitcoiner movement is what is needed. Educational grants through organizations like Bitcoin Majlis should be funded with endowments. Local Muslim bitcoin meetups must form around community mosques and Islamic 3rd spaces. Networked together, each community would be like decentralized nodes that could function as a seed-holder for a multi-sig waqf that can circulate wealth to those that need it, giving the poorer a real opportunity to level up and contribute to societ and demonstrating why zakat is superior to interest.
Organic, marginal organizing must be the foundation to building sovereignty within the Ummah. Sovereignty starts at the individual level and not just for all spiritual devotion, but for economics as well. Physical sovereignty is in the individual human choice and action of the Muslim. It is the direct responsibility placed upon insan when the trust of khalifa was placed upon him. Sovereignty is the hallmark of our covenant, we must embrace our right to self-determination and secede from a monetary policy of riba back toward that which is pure.
"Whatever loans you give, seeking interest at the expense of people’s wealth will not increase with Allah. But whatever charity you give, seeking the pleasure of Allah—it is they whose reward will be multiplied." (Quran 30:39)
FAQ
Why does bitcoin have any value?
Unlike stocks, bonds, real-estate or even commodities such as oil and wheat, bitcoins cannot be valued using standard discounted cash-flow analysis or by demand for their use in the production of higher order goods. Bitcoins fall into an entirely different category of goods, known as monetary goods, whose value is set game-theoretically. I.e., each market participant values the good based on their appraisal of whether and how much other participants will value it. The truth is that the notions of “cheap” and “expensive” are essentially meaningless in reference to monetary goods. The price of a monetary good is not a reflection of its cash flow or how useful it is but, rather, is a measure of how widely adopted it has become for the various roles of money.
Is crypto-currency halal?
It is important to note that this paper argues in favor of Bitcoin, not “Crypto” because all other crypto coins are simply attempts a re-introducing fiat money-creation in digital space. Since they fail to address the root cause error of riba they will ultimately be either destroyed by governments or governments will evolve to embrace them in attempts to modernize their current fiat system. To highlight this, one can call it “bit-power” rather than “bit-coin” and see that there is more at play here with bitcoin than current systems contain. Mufti Faraz Adam’s fatwa from 2017 regarding cryptocurrency adaqately addresses general permissibility. However, bitcoin has evolved much since then and is on track to achieve global recognition as money in the next few years. It is also vital to note that monetary policy is understood by governments as a vehicle for sanctions and a tool in a political war-chest. Bitcoin evolves beyond this as at its backing is literal energy from CPU mining that goes beyond kinetic power projection limitations into cyberspace. For more on theories of bitcoin’s potential as a novel weapons technology see Jason Lowery’s book Softwar.
What about market volatility?
Since the inception of the first exchange traded price in 2010, the bitcoin market has witnessed five major Gartner hype cycles. It is worth observing that the rise in bitcoin’s price during hype cycles is largely correlated with an increase in liquidity and the ease with which investors could purchase bitcoins. Although it is impossible to predict the exact magnitude of the current hype cycle, it would be reasonable to conjecture that the current cycle reaches its zenith in the range of $115,000 to $170,000. Bitcoin’s final Gartner hype cycle will begin when nation-states start accumulating it as a part of their foreign currency reserves. As private sector interest increases the capitalization of Bitcoin has exceeded 1 trillion dollars which is generally considered the threshold at which an assest becomes liquid enough for most states to enter the market. In fact, El Salvador is already on board.
-
 @ f57bac88:6045161e
2025-04-18 19:23:24
@ f57bac88:6045161e
2025-04-18 19:23:24در دنیای امروز، بارها دیدهایم که بهخاطر یک کار خوب، یک سخن درست یا گذشتهای درخشان، کسی را روی سکوی قهرمانی میگذاریم و او را بینقص و مطلق میپنداریم. اما حقیقت این است که هیچ انسانی کامل نیست. آدمها موجوداتی پیچیدهاند که با گذر زمان، تجربه و شرایط، تغییر میکنند. آنچه امروز ستودنی است، لزوماً فردا هم همان ارزش را ندارد.
برای مثال، توماج صالحی را در نظر بگیرید؛ کسی که با صدای بلند از حق مردم گفت، شعر خواند و در زندان و زیر فشار شکنجه مقاومت کرد. شجاعت او شایسته تحسین است، اما نمیتوان انتظار داشت که تحت چنین فشار طاقتفرسایی، همیشه همان تصویر قهرمانانه را حفظ کند. یا مسیح علینژاد که علیه جمهوری اسلامی سخن گفت و کارهایی کرد که بسیاری آن را ارزشمند میدانند. اما این به آن معنا نیست که هر تصمیم یا سخنی از او بینقص است یا او ذاتاً بیعیب است. حتی خاندان پهلوی که زمانی نماد پیشرفت و مدرنیته بودند، نمیتوانند بهتنهایی معیار حقیقت یا ناجی یک ملت باشند.
این ماجرا به چهرههای سیاسی و تاریخی محدود نمیشود. ارنستو چگوارا برای بسیاری نماد مبارزه و آزادی است، اما وقتی دقیقتر نگاه کنیم، میبینیم برخی تصمیماتش به ضرر مردم تمام شد. در زندگی روزمره هم همینطور است؛ ممکن است کسی در لحظهای خاص کاری درست انجام دهد، اما این دلیل نمیشود که همیشه شایسته اعتماد بیچونوچرا باشد.
بتسازی از آدمها خطر بزرگی دارد: وقتی کسی را اسطوره میکنیم، دیگر نمیتوانیم نقصها و اشتباهاتش را ببینیم. اگر روزی خطایی از او سر بزند، یا شوکه میشویم یا به هر بهانهای سعی میکنیم آن را توجیه کنیم. این روند، ما را از قضاوت منصفانه و خردمندانه دور میکند و به جای حقیقت، به توهم وابستهمان میسازد.
به جای بتسازی، بهتر است انسانها را همانگونه که هستند ببینیم: با خوبیها و کاستیها، با شجاعتها و ضعفها. اگر کسی کار درستی کرد، تحسینش کنیم، اما نگذاریم این تحسین، چشممان را روی حقیقت ببندد. این نگاه نهتنها ما را از سرخوردگی و توهم دور نگه میدارد، بلکه قدرت تحلیل و یادگیریمان را تقویت میکند.
اما آزادی واقعی چگونه به دست میآید؟ آزادی حقیقی در انتظار منجی یا قهرمان نیست. آزادی زمانی معنا پیدا میکند که هر فرد، خود قدرت انتخاب، تفکر و عمل داشته باشد. به جای وابستگی به یک نفر یا یک گروه، باید سیستمی غیرمتمرکز و آزاد ایجاد کنیم که در آن هیچکس تحت سلطه دیگری نباشد. همانطور که شهبانو فرح پهلوی گفته است: «همیشه نور بر تاریکی پیروز است.» این نور، نماد خرد جمعی و آزادی است که با اتکا به خود و همکاری با دیگران، تاریکی جهل و استبداد را از بین میبرد.
در نهایت، به جای پرستش قهرمانهای خیالی، بیایید ارزشها و ایدهها را مستقل از آدمها بسنجیم. با عمل آزادانه، نقد منصفانه و همکاری جمعی، میتوانیم راه را برای جامعهای عادلانه، آزاد و روشن هموار کنیم.
-
 @ 7d33ba57:1b82db35
2025-04-18 19:17:15
@ 7d33ba57:1b82db35
2025-04-18 19:17:15Panama City is a bold fusion of colonial charm, tropical coastline, and modern skyline—the only capital in the world with a rainforest inside city limits. It's where skyscrapers meet historic plazas, and just minutes from one of the greatest engineering marvels on Earth: the Panama Canal.
🏙️ Top Things to Do in Panama City
🛕 Casco Viejo (Old Quarter)
- A UNESCO-listed historic district with Spanish colonial architecture, vibrant cafés, and rooftop bars
- Walk the cobblestone streets, visit Plaza de Francia, and sip cocktails overlooking the bay
- Perfect spot for nightlife, art galleries, and boutique hotels
🌉 Panama Canal
- Visit the Miraflores Locks to watch ships rise and fall as they pass between oceans
- The Canal Museum explains its incredible history and global impact
- Want a deeper experience? Take a partial or full canal transit boat tour
🐒 Metropolitan Natural Park
- A rainforest just 10 minutes from downtown
- Hike trails with sloths, monkeys, and incredible views of the city skyline from lookout points
🚴 Cinta Costera & Amador Causeway
- Coastal promenades ideal for biking or strolling
- Head to the Biomuseo, designed by Frank Gehry, or catch a sunset with city views on the Causeway
🌴 Day Trips & Getaways
🏝️ San Blas Islands
- Idyllic Caribbean islands run by the Guna Yala people
- Crystal-clear waters, white sands, no crowds—perfect for a tropical escape
🐬 Taboga Island
- Just 30 minutes by ferry
- Known as the “Island of Flowers,” it’s great for swimming, hiking, and beach relaxation
🍽️ What to Eat in Panama City
- Ceviche – Grab some fresh at the Mercado de Mariscos (Fish Market)
- Sancocho – A hearty chicken and root vegetable soup
- Ropa Vieja – Shredded beef stew, often served with rice and plantains
- Don’t miss local coffee, craft beer, and rum cocktails with a view
📅 Best Time to Visit
- Dry Season (Mid-Dec–April): Best for sightseeing, canal tours, and island trips
- Wet Season (May–Nov): Expect brief afternoon showers, but still very green and vibrant
✈️ Getting There & Around
- Tocumen International Airport (PTY) connects to major global cities
- Uber and taxis are common, but Casco Viejo is best explored on foot
- Use the Metro or MiBus for budget-friendly public transport
-
 @ 71550e6c:b64c37a9
2025-03-29 10:55:55
@ 71550e6c:b64c37a9
2025-03-29 10:55:55Just do the same as this video shows.
Here's the video: https://cdn.azzamo.net/7cdcc2718f1e15eb03e323f62e07582b4001da273aa5c21475d680f02b32f0e9.mp4
One caveat: do not trust the draft will be kept here after you close
nak fs. Wait, no, it definitely won't stay here, but I'm not even sure it will stay here if you only navigate away and come back later, FUSE is weird and I didn't test.But at least it should work for copy-pasting. Or writing everything in one go.
-
 @ a60e79e0:1e0e6813
2025-03-28 08:47:35
@ a60e79e0:1e0e6813
2025-03-28 08:47:35This is a long form note of a post that lives on my Nostr educational website Hello Nostr.
When most people stumble across Nostr, they see is as a 'decentralized social media alternative' — something akin to Twitter (X), but free from corporate control. But the full name, "Notes and Other Stuff Transmitted by Relays", gives a clue that there’s more to it than just posting short messages. The 'notes' part is easy to grasp because it forms almost everyone's first touch point with the protocol. But the 'other stuff'? That’s where Nostr really gets exciting. The 'other stuff' is all the creative and experimental things people are building on Nostr, beyond simple text based notes.
Every action on Nostr is an event, a like, a post, a profile update, or even a payment. The 'Kind' is what specifies the purpose of each event. Kinds are the building blocks of how information is categorized and processed on the network, and the most popular become part of higher lever specification guidelines known as Nostr Implementation Possibility - NIP. A NIP is a document that defines how something in Nostr should work, including the rules, standards, or features. NIPs define the type of 'other stuff' that be published and displayed by different styles of client to meet different purposes.
Nostr isn’t locked into a single purpose. It’s a foundation for whatever 'other stuff' you can dream up.
Types of Other Stuff
The 'other stuff' name is intentionally vague. Why? Because the possibilities of what can fall under this category are quite literally limitless. In the short time since Nostr's inception, the number of sub-categories that have been built on top of the Nostr's open protocol is mind bending. Here are a few examples:
- Long-Form Content: Think blog posts or articles. NIP-23.
- Private Messaging: Encrypted chats between users. NIP-04.
- Communities: Group chats or forums like Reddit. NIP-72
- Marketplaces: People listing stuff for sale, payable with zaps. NIP-15
- Zaps: Value transfer over the Lightning Network. NIP57

Popular 'Other Stuff' Clients
Here's a short list of some of the most recent and popular apps and clients that branch outside of the traditional micro-blogging use case and leverage the openness, and interoperability that Nostr can provide.
Blogging (Long Form Content)
- Habla - Web app for Nostr based blogs
- Highlighter - Web app that enables users to highlight, store and share content
Group Chats
- Chachi Chat - Relay-based (NIP-29) group chat client
- 0xchat - Mobile based secure chat
- Flotilla - Web based chat app built for self-hosted communities
- Nostr Nests - Web app for audio chats
- White Noise - Mobile based secure chat
Marketplaces
- Shopstr - Permissionless marketplace for web
- Plebeian Market - Permissionless marketplace for web
- LNBits Market - Permissionless marketplace for your node
- Mostro - Nostr based Bitcoin P2P Marketplace
Photo/Video
Music
- Fountain - Podcast app with Nostr features
- Wavlake - A music app supporting the value-for-value ecosystem
Livestreaming
- Zap.stream - Nostr native live streams
Misc
- Wikifreedia - Nostr based Wikipedia alternative
- Wikistr - Nostr based Wikipedia alternative
- Pollerama - Nostr based polls
- Zap Store - The app store powered by your social graph
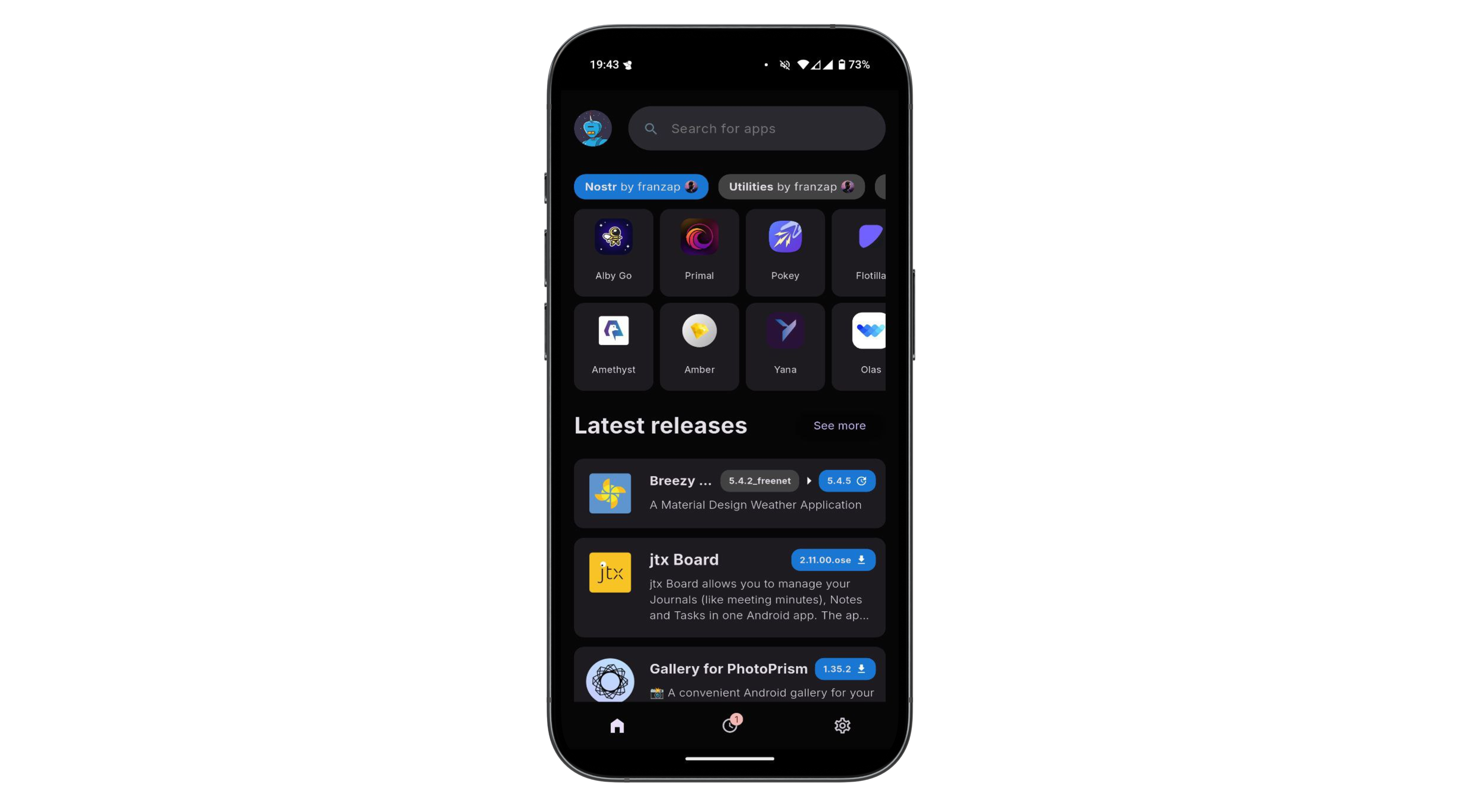
The 'other stuff' in Nostr is what makes it special. It’s not just about replacing Twitter or Facebook, it’s about building a decentralized ecosystem where anything from private chats to marketplaces can thrive. The beauty of Nostr is that it’s a flexible foundation. Developers can dream up new ideas and build them into clients, and the relays just keep humming along, passing the data around. It’s still early days, so expect the 'other stuff' to grow wilder and weirder over time!
You can explore the evergrowing 'other stuff' ecosystem at NostrApps.com, Nostr.net and Awesome Nostr.
-
 @ 7d33ba57:1b82db35
2025-04-18 19:03:21
@ 7d33ba57:1b82db35
2025-04-18 19:03:21Perched high above the Danube River in Donaustauf, just east of Regensburg, the Walhalla Memorial is one of Germany’s most unique and impressive landmarks. Inspired by the Parthenon in Athens, this neoclassical temple was built in the 19th century by order of King Ludwig I of Bavaria to honor great Germans from history.
🏛️ What Is Walhalla?
- A massive white marble temple that resembles an ancient Greek sanctuary
- Completed in 1842, it was named after the Norse “Valhalla” — the hall of heroes
- Inside, you’ll find over 130 busts and plaques of notable figures in German culture, science, politics, and the arts
- Honorees include Albert Einstein, Ludwig van Beethoven, Johann Wolfgang von Goethe, and more
📸 Why Visit?
- Panoramic views of the Danube valley—especially stunning at sunset
- The architecture and symmetry of the monument are jaw-dropping
- It’s a peaceful, reflective spot with lots of photo opportunities
- Learn about German and European history in a serene, scenic setting
🚶♀️ How to Get There
- 8 km (5 miles) from Regensburg—about 15 minutes by car or bus
- You can also bike along the Danube path (Donau-Radweg), a beautiful riverside ride
- Once you arrive, be ready to climb a long flight of stone steps to reach the top
🕰️ Tips for Visiting
- Best in spring to early fall, when the surrounding hills are lush and green
- Bring water and comfortable shoes for the climb
- The interior is open to visitors (small entrance fee)
- Combine it with a stop in Regensburg or Weltenburg Abbey for a perfect day trip
-
 @ 91bea5cd:1df4451c
2025-04-15 06:23:35
@ 91bea5cd:1df4451c
2025-04-15 06:23:35Um bom gerenciamento de senhas deve ser simples e seguir a filosofia do Unix. Organizado em hierarquia e fácil de passar de um computador para outro.
E por isso não é recomendável o uso de aplicativos de terceiros que tenham acesso a suas chaves(senhas) em seus servidores, tampouco as opções nativas dos navegadores, que também pertencem a grandes empresas que fazem um grande esforço para ter acesso a nossas informações.
Recomendação
- pass
- Qtpass (gerenciador gráfico)
Com ele seus dados são criptografados usando sua chave gpg e salvo em arquivos organizados por pastas de forma hierárquica, podendo ser integrado a um serviço git de sua escolha ou copiado facilmente de um local para outro.
Uso
O seu uso é bem simples.
Configuração:
pass git initPara ver:
pass Email/example.comCopiar para área de transferência (exige xclip):
pass -c Email/example.comPara inserir:
pass insert Email/example0.comPara inserir e gerar senha:
pass generate Email/example1.comPara inserir e gerar senha sem símbolos:
pass generate --no-symbols Email/example1.comPara inserir, gerar senha e copiar para área de transferência :
pass generate -c Email/example1.comPara remover:
pass rm Email/example.com -
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ 7d33ba57:1b82db35
2025-04-18 18:46:56
@ 7d33ba57:1b82db35
2025-04-18 18:46:56Regensburg is a UNESCO World Heritage city and one of Germany’s most beautifully preserved medieval towns. Nestled on the Danube River in Bavaria, this lively university city blends 2,000 years of history with a fresh, modern vibe—perfect for lovers of architecture, riverside cafés, and old-world charm.
🏰 Top Things to Do in Regensburg
🌉 Stone Bridge (Steinerne Brücke)
- Built in the 12th century and still standing strong
- Offers sweeping views of the old town and river
- Once the only crossing of the Danube for hundreds of miles
⛪ Regensburg Cathedral (Dom St. Peter)
- A towering masterpiece of Gothic architecture
- Home to the Regensburger Domspatzen, one of the world’s oldest boys’ choirs
- Intricate stained glass and dramatic spires—don’t miss it!
🏛️ Old Town (Altstadt)
- Winding alleys, colorful facades, Roman ruins, and medieval towers
- Full of hidden courtyards, shops, and traditional Bavarian restaurants
- Look for the Porta Praetoria, a Roman gate from 179 AD
🏰 St. Emmeram's Abbey & Thurn and Taxis Palace
- A former Benedictine monastery turned into a princely palace
- Guided tours show the lavish rooms and tell tales of European royalty
- The family still lives there today!
🍽️ What to Eat & Drink
- Regensburger Wurst – A smoky local sausage, often grilled
- Grab a bite at the Historic Sausage Kitchen (Wurstkuchl), open since the 1100s!
- Pair your meal with a Bavarian beer from Weltenburg or Spital Brewery
🚶♀️ Riverside Walks & Day Trips
- Stroll or bike along the Danube Promenade for peaceful views
- Take a boat trip to Walhalla, a neoclassical temple overlooking the river
- Visit Weltenburg Abbey, the oldest monastic brewery in the world, nestled in the Danube Gorge
📅 Best Time to Visit
- May–September: Ideal weather, open-air events, and vibrant street life
- December: Magical Christmas markets with mulled wine and lights in the medieval square
- Shoulder seasons: Quieter, but still gorgeous
🛤️ Getting There
- Just 1.5 hours by train from Munich
- The old town is compact and walkable—no car needed
-
 @ 91bea5cd:1df4451c
2025-04-15 06:19:19
@ 91bea5cd:1df4451c
2025-04-15 06:19:19O que é Tahoe-LAFS?
Bem-vindo ao Tahoe-LAFS_, o primeiro sistema de armazenamento descentralizado com
- Segurança independente do provedor * .
Tahoe-LAFS é um sistema que ajuda você a armazenar arquivos. Você executa um cliente Programa no seu computador, que fala com um ou mais servidores de armazenamento em outros computadores. Quando você diz ao seu cliente para armazenar um arquivo, ele irá criptografar isso Arquivo, codifique-o em múltiplas peças, depois espalhe essas peças entre Vários servidores. As peças são todas criptografadas e protegidas contra Modificações. Mais tarde, quando você pede ao seu cliente para recuperar o arquivo, ele irá Encontre as peças necessárias, verifique se elas não foram corrompidas e remontadas Eles, e descriptografar o resultado.
O cliente cria mais peças (ou "compartilhamentos") do que acabará por precisar, então Mesmo que alguns servidores falhem, você ainda pode recuperar seus dados. Corrompido Os compartilhamentos são detectados e ignorados, de modo que o sistema pode tolerar o lado do servidor Erros no disco rígido. Todos os arquivos são criptografados (com uma chave exclusiva) antes Uploading, então mesmo um operador de servidor mal-intencionado não pode ler seus dados. o A única coisa que você pede aos servidores é que eles podem (geralmente) fornecer o Compartilha quando você os solicita: você não está confiando sobre eles para Confidencialidade, integridade ou disponibilidade absoluta.
O que é "segurança independente do provedor"?
Todo vendedor de serviços de armazenamento na nuvem irá dizer-lhe que o seu serviço é "seguro". Mas o que eles significam com isso é algo fundamentalmente diferente Do que queremos dizer. O que eles significam por "seguro" é que depois de ter dado Eles o poder de ler e modificar seus dados, eles tentam muito difícil de não deixar Esse poder seja abusado. Isso acaba por ser difícil! Insetos, Configurações incorretas ou erro do operador podem acidentalmente expor seus dados para Outro cliente ou para o público, ou pode corromper seus dados. Criminosos Ganho rotineiramente de acesso ilícito a servidores corporativos. Ainda mais insidioso é O fato de que os próprios funcionários às vezes violam a privacidade do cliente De negligência, avareza ou mera curiosidade. O mais consciencioso de Esses prestadores de serviços gastam consideráveis esforços e despesas tentando Mitigar esses riscos.
O que queremos dizer com "segurança" é algo diferente. * O provedor de serviços Nunca tem a capacidade de ler ou modificar seus dados em primeiro lugar: nunca. * Se você usa Tahoe-LAFS, então todas as ameaças descritas acima não são questões para você. Não só é fácil e barato para o provedor de serviços Manter a segurança de seus dados, mas na verdade eles não podem violar sua Segurança se eles tentaram. Isto é o que chamamos de * independente do fornecedor segurança*.
Esta garantia está integrada naturalmente no sistema de armazenamento Tahoe-LAFS e Não exige que você execute um passo de pré-criptografia manual ou uma chave complicada gestão. (Afinal, ter que fazer operações manuais pesadas quando Armazenar ou acessar seus dados anularia um dos principais benefícios de Usando armazenamento em nuvem em primeiro lugar: conveniência.)
Veja como funciona:
Uma "grade de armazenamento" é constituída por uma série de servidores de armazenamento. Um servidor de armazenamento Tem armazenamento direto em anexo (tipicamente um ou mais discos rígidos). Um "gateway" Se comunica com os nós de armazenamento e os usa para fornecer acesso ao Rede sobre protocolos como HTTP (S), SFTP ou FTP.
Observe que você pode encontrar "cliente" usado para se referir aos nós do gateway (que atuam como Um cliente para servidores de armazenamento) e também para processos ou programas que se conectam a Um nó de gateway e operações de execução na grade - por exemplo, uma CLI Comando, navegador da Web, cliente SFTP ou cliente FTP.
Os usuários não contam com servidores de armazenamento para fornecer * confidencialidade * nem
- Integridade * para seus dados - em vez disso, todos os dados são criptografados e Integridade verificada pelo gateway, para que os servidores não possam ler nem Modifique o conteúdo dos arquivos.
Os usuários dependem de servidores de armazenamento para * disponibilidade *. O texto cifrado é Codificado por apagamento em partes
Ndistribuídas em pelo menosHdistintas Servidores de armazenamento (o valor padrão paraNé 10 e paraHé 7) então Que pode ser recuperado de qualquerKdesses servidores (o padrão O valor deKé 3). Portanto, apenas a falha doH-K + 1(com o Padrões, 5) servidores podem tornar os dados indisponíveis.No modo de implantação típico, cada usuário executa seu próprio gateway sozinho máquina. Desta forma, ela confia em sua própria máquina para a confidencialidade e Integridade dos dados.
Um modo de implantação alternativo é que o gateway é executado em uma máquina remota e O usuário se conecta ao HTTPS ou SFTP. Isso significa que o operador de O gateway pode visualizar e modificar os dados do usuário (o usuário * depende de * o Gateway para confidencialidade e integridade), mas a vantagem é que a O usuário pode acessar a grade Tahoe-LAFS com um cliente que não possui o Software de gateway instalado, como um quiosque de internet ou celular.
Controle de acesso
Existem dois tipos de arquivos: imutáveis e mutáveis. Quando você carrega um arquivo Para a grade de armazenamento, você pode escolher o tipo de arquivo que será no grade. Os arquivos imutáveis não podem ser modificados quando foram carregados. UMA O arquivo mutable pode ser modificado por alguém com acesso de leitura e gravação. Um usuário Pode ter acesso de leitura e gravação a um arquivo mutable ou acesso somente leitura, ou não Acesso a ele.
Um usuário que tenha acesso de leitura e gravação a um arquivo mutable ou diretório pode dar Outro acesso de leitura e gravação do usuário a esse arquivo ou diretório, ou eles podem dar Acesso somente leitura para esse arquivo ou diretório. Um usuário com acesso somente leitura Para um arquivo ou diretório pode dar acesso a outro usuário somente leitura.
Ao vincular um arquivo ou diretório a um diretório pai, você pode usar um Link de leitura-escrita ou um link somente de leitura. Se você usar um link de leitura e gravação, então Qualquer pessoa que tenha acesso de leitura e gravação ao diretório pai pode obter leitura-escrita Acesso à criança e qualquer pessoa que tenha acesso somente leitura ao pai O diretório pode obter acesso somente leitura à criança. Se você usar uma leitura somente Link, qualquer pessoa que tenha lido-escrito ou acesso somente leitura ao pai O diretório pode obter acesso somente leitura à criança.
================================================== ==== Usando Tahoe-LAFS com uma rede anônima: Tor, I2P ================================================== ====
. `Visão geral '
. `Casos de uso '
.
Software Dependencies_#.
Tor#.I2P. `Configuração de conexão '
. `Configuração de Anonimato '
#.
Anonimato do cliente ' #.Anonimato de servidor, configuração manual ' #. `Anonimato de servidor, configuração automática '. `Problemas de desempenho e segurança '
Visão geral
Tor é uma rede anonimização usada para ajudar a esconder a identidade da Internet Clientes e servidores. Consulte o site do Tor Project para obter mais informações: Https://www.torproject.org/
I2P é uma rede de anonimato descentralizada que se concentra no anonimato de ponta a ponta Entre clientes e servidores. Consulte o site I2P para obter mais informações: Https://geti2p.net/
Casos de uso
Existem três casos de uso potenciais para Tahoe-LAFS do lado do cliente:
-
O usuário deseja sempre usar uma rede de anonimato (Tor, I2P) para proteger Seu anonimato quando se conecta às redes de armazenamento Tahoe-LAFS (seja ou Não os servidores de armazenamento são anônimos).
-
O usuário não se preocupa em proteger seu anonimato, mas eles desejam se conectar a Servidores de armazenamento Tahoe-LAFS que são acessíveis apenas através de Tor Hidden Services ou I2P.
-
Tor é usado apenas se uma sugestão de conexão do servidor usar
tor:. Essas sugestões Geralmente tem um endereço.onion. -
I2P só é usado se uma sugestão de conexão do servidor usa
i2p:. Essas sugestões Geralmente têm um endereço.i2p. -
O usuário não se preocupa em proteger seu anonimato ou para se conectar a um anonimato Servidores de armazenamento. Este documento não é útil para você ... então pare de ler.
Para servidores de armazenamento Tahoe-LAFS existem três casos de uso:
-
O operador deseja proteger o anonimato fazendo seu Tahoe Servidor acessível apenas em I2P, através de Tor Hidden Services, ou ambos.
-
O operador não * requer * anonimato para o servidor de armazenamento, mas eles Quer que ele esteja disponível tanto no TCP / IP roteado publicamente quanto através de um Rede de anonimização (I2P, Tor Hidden Services). Uma possível razão para fazer Isso é porque ser alcançável através de uma rede de anonimato é um Maneira conveniente de ignorar NAT ou firewall que impede roteios públicos Conexões TCP / IP ao seu servidor (para clientes capazes de se conectar a Tais servidores). Outro é o que torna o seu servidor de armazenamento acessível Através de uma rede de anonimato pode oferecer uma melhor proteção para sua Clientes que usam essa rede de anonimato para proteger seus anonimato.
-
O operador do servidor de armazenamento não se preocupa em proteger seu próprio anonimato nem Para ajudar os clientes a proteger o deles. Pare de ler este documento e execute Seu servidor de armazenamento Tahoe-LAFS usando TCP / IP com roteamento público.
Veja esta página do Tor Project para obter mais informações sobre Tor Hidden Services: Https://www.torproject.org/docs/hidden-services.html.pt
Veja esta página do Projeto I2P para obter mais informações sobre o I2P: Https://geti2p.net/en/about/intro
Dependências de software
Tor
Os clientes que desejam se conectar a servidores baseados em Tor devem instalar o seguinte.
-
Tor (tor) deve ser instalado. Veja aqui: Https://www.torproject.org/docs/installguide.html.en. No Debian / Ubuntu, Use
apt-get install tor. Você também pode instalar e executar o navegador Tor Agrupar. -
Tahoe-LAFS deve ser instalado com o
[tor]"extra" habilitado. Isso vai Instaletxtorcon::
Pip install tahoe-lafs [tor]
Os servidores Tor-configurados manualmente devem instalar Tor, mas não precisam
Txtorconou o[tor]extra. Configuração automática, quando Implementado, vai precisar destes, assim como os clientes.I2P
Os clientes que desejam se conectar a servidores baseados em I2P devem instalar o seguinte. Tal como acontece com Tor, os servidores baseados em I2P configurados manualmente precisam do daemon I2P, mas Não há bibliotecas especiais de apoio Tahoe-side.
-
I2P deve ser instalado. Veja aqui: Https://geti2p.net/en/download
-
A API SAM deve estar habilitada.
-
Inicie o I2P.
- Visite http://127.0.0.1:7657/configclients no seu navegador.
- Em "Configuração do Cliente", marque a opção "Executar no Startup?" Caixa para "SAM Ponte de aplicação ".
- Clique em "Salvar Configuração do Cliente".
-
Clique no controle "Iniciar" para "ponte de aplicação SAM" ou reinicie o I2P.
-
Tahoe-LAFS deve ser instalado com o
[i2p]extra habilitado, para obterTxi2p::
Pip install tahoe-lafs [i2p]
Tor e I2P
Os clientes que desejam se conectar a servidores baseados em Tor e I2P devem instalar tudo acima. Em particular, Tahoe-LAFS deve ser instalado com ambos Extras habilitados ::
Pip install tahoe-lafs [tor, i2p]
Configuração de conexão
Consulte: ref:
Connection Managementpara uma descrição do[tor]e[I2p]seções detahoe.cfg. Estes controlam como o cliente Tahoe Conecte-se a um daemon Tor / I2P e, assim, faça conexões com Tor / I2P-baseadas Servidores.As seções
[tor]e[i2p]só precisam ser modificadas para serem usadas de forma incomum Configurações ou para habilitar a configuração automática do servidor.A configuração padrão tentará entrar em contato com um daemon local Tor / I2P Ouvindo as portas usuais (9050/9150 para Tor, 7656 para I2P). Enquanto Há um daemon em execução no host local e o suporte necessário Bibliotecas foram instaladas, os clientes poderão usar servidores baseados em Tor Sem qualquer configuração especial.
No entanto, note que esta configuração padrão não melhora a Anonimato: as conexões TCP normais ainda serão feitas em qualquer servidor que Oferece um endereço regular (cumpre o segundo caso de uso do cliente acima, não o terceiro). Para proteger o anonimato, os usuários devem configurar o
[Connections]da seguinte maneira:[Conexões] Tcp = tor
Com isso, o cliente usará Tor (em vez de um IP-address -reviração de conexão direta) para alcançar servidores baseados em TCP.
Configuração de anonimato
Tahoe-LAFS fornece uma configuração "flag de segurança" para indicar explicitamente Seja necessário ou não a privacidade do endereço IP para um nó ::
[nó] Revelar-IP-address = (booleano, opcional)
Quando
revelar-IP-address = False, Tahoe-LAFS se recusará a iniciar se algum dos As opções de configuração emtahoe.cfgrevelariam a rede do nó localização:-
[Conexões] tcp = toré necessário: caso contrário, o cliente faria Conexões diretas para o Introdução, ou qualquer servidor baseado em TCP que aprende Do Introdutor, revelando seu endereço IP para esses servidores e um Rede de espionagem. Com isso, Tahoe-LAFS só fará Conexões de saída através de uma rede de anonimato suportada. -
Tub.locationdeve ser desativado ou conter valores seguros. este O valor é anunciado para outros nós através do Introdutor: é como um servidor Anuncia sua localização para que os clientes possam se conectar a ela. No modo privado, ele É um erro para incluir umtcp:dica notub.location. Modo privado Rejeita o valor padrão detub.location(quando a chave está faltando Inteiramente), que éAUTO, que usaifconfigpara adivinhar o nó Endereço IP externo, o que o revelaria ao servidor e a outros clientes.
Esta opção é ** crítica ** para preservar o anonimato do cliente (cliente Caso de uso 3 de "Casos de uso", acima). Também é necessário preservar uma Anonimato do servidor (caso de uso do servidor 3).
Esse sinalizador pode ser configurado (para falso), fornecendo o argumento
--hide-ippara Os comandoscreate-node,create-clientoucreate-introducer.Observe que o valor padrão de
revelar-endereço IPé verdadeiro, porque Infelizmente, esconder o endereço IP do nó requer software adicional para ser Instalado (conforme descrito acima) e reduz o desempenho.Anonimato do cliente
Para configurar um nó de cliente para anonimato,
tahoe.cfg** deve ** conter o Seguindo as bandeiras de configuração ::[nó] Revelar-IP-address = False Tub.port = desativado Tub.location = desativado
Uma vez que o nodo Tahoe-LAFS foi reiniciado, ele pode ser usado anonimamente (cliente Caso de uso 3).
Anonimato do servidor, configuração manual
Para configurar um nó de servidor para ouvir em uma rede de anonimato, devemos primeiro Configure Tor para executar um "Serviço de cebola" e encaminhe as conexões de entrada para o Porto Tahoe local. Então, configuramos Tahoe para anunciar o endereço
.onionAos clientes. Também configuramos Tahoe para não fazer conexões TCP diretas.- Decida em um número de porta de escuta local, chamado PORT. Isso pode ser qualquer não utilizado Porta de cerca de 1024 até 65535 (dependendo do kernel / rede do host Config). Nós diremos a Tahoe para escutar nesta porta, e nós diremos a Tor para Encaminhe as conexões de entrada para ele.
- Decida em um número de porta externo, chamado VIRTPORT. Isso será usado no Localização anunciada e revelada aos clientes. Pode ser qualquer número de 1 Para 65535. Pode ser o mesmo que PORT, se quiser.
- Decida em um "diretório de serviço oculto", geralmente em
/ var / lib / tor / NAME. Pediremos a Tor para salvar o estado do serviço de cebola aqui, e Tor irá Escreva o endereço.onionaqui depois que ele for gerado.
Em seguida, faça o seguinte:
-
Crie o nó do servidor Tahoe (com
tahoe create-node), mas não ** não ** Lança-o ainda. -
Edite o arquivo de configuração Tor (normalmente em
/ etc / tor / torrc). Precisamos adicionar Uma seção para definir o serviço oculto. Se nossa PORT for 2000, VIRTPORT é 3000, e estamos usando/ var / lib / tor / tahoecomo o serviço oculto Diretório, a seção deve se parecer com ::HiddenServiceDir / var / lib / tor / tahoe HiddenServicePort 3000 127.0.0.1:2000
-
Reinicie Tor, com
systemctl restart tor. Aguarde alguns segundos. -
Leia o arquivo
hostnameno diretório de serviço oculto (por exemplo,/ Var / lib / tor / tahoe / hostname). Este será um endereço.onion, comoU33m4y7klhz3b.onion. Ligue para esta CEBOLA. -
Edite
tahoe.cfgpara configurartub.portpara usarTcp: PORT: interface = 127.0.0.1etub.locationpara usarTor: ONION.onion: VIRTPORT. Usando os exemplos acima, isso seria ::[nó] Revelar-endereço IP = falso Tub.port = tcp: 2000: interface = 127.0.0.1 Tub.location = tor: u33m4y7klhz3b.onion: 3000 [Conexões] Tcp = tor
-
Inicie o servidor Tahoe com
tahoe start $ NODEDIR
A seção
tub.portfará com que o servidor Tahoe ouça no PORT, mas Ligue o soquete de escuta à interface de loopback, que não é acessível Do mundo exterior (mas * é * acessível pelo daemon Tor local). Então o A seçãotcp = torfaz com que Tahoe use Tor quando se conecta ao Introdução, escondendo o endereço IP. O nó se anunciará a todos Clientes que usam `tub.location``, então os clientes saberão que devem usar o Tor Para alcançar este servidor (e não revelar seu endereço IP através do anúncio). Quando os clientes se conectam ao endereço da cebola, seus pacotes serão Atravessar a rede de anonimato e eventualmente aterrar no Tor local Daemon, que então estabelecerá uma conexão com PORT no localhost, que é Onde Tahoe está ouvindo conexões.Siga um processo similar para construir um servidor Tahoe que escuta no I2P. o O mesmo processo pode ser usado para ouvir tanto o Tor como o I2P (
tub.location = Tor: ONION.onion: VIRTPORT, i2p: ADDR.i2p). Também pode ouvir tanto Tor como TCP simples (caso de uso 2), comtub.port = tcp: PORT,tub.location = Tcp: HOST: PORT, tor: ONION.onion: VIRTPORTeanonymous = false(e omite A configuraçãotcp = tor, já que o endereço já está sendo transmitido através de O anúncio de localização).Anonimato do servidor, configuração automática
Para configurar um nó do servidor para ouvir em uma rede de anonimato, crie o Nó com a opção
--listen = tor. Isso requer uma configuração Tor que Ou lança um novo daemon Tor, ou tem acesso à porta de controle Tor (e Autoridade suficiente para criar um novo serviço de cebola). Nos sistemas Debian / Ubuntu, façaApt install tor, adicione-se ao grupo de controle comadduser YOURUSERNAME debian-tore, em seguida, inicie sessão e faça o login novamente: se osgroupsO comando incluidebian-torna saída, você deve ter permissão para Use a porta de controle de domínio unix em/ var / run / tor / control.Esta opção irá definir
revelar-IP-address = Falsee[connections] tcp = Tor. Ele alocará as portas necessárias, instruirá Tor para criar a cebola Serviço (salvando a chave privada em algum lugar dentro de NODEDIR / private /), obtenha O endereço.onione preenchatub.portetub.locationcorretamente.Problemas de desempenho e segurança
Se você estiver executando um servidor que não precisa ser Anônimo, você deve torná-lo acessível através de uma rede de anonimato ou não? Ou você pode torná-lo acessível * ambos * através de uma rede de anonimato E como um servidor TCP / IP rastreável publicamente?
Existem várias compensações efetuadas por esta decisão.
Penetração NAT / Firewall
Fazer com que um servidor seja acessível via Tor ou I2P o torna acessível (por Clientes compatíveis com Tor / I2P) mesmo que existam NAT ou firewalls que impeçam Conexões TCP / IP diretas para o servidor.
Anonimato
Tornar um servidor Tahoe-LAFS acessível * somente * via Tor ou I2P pode ser usado para Garanta que os clientes Tahoe-LAFS usem Tor ou I2P para se conectar (Especificamente, o servidor só deve anunciar endereços Tor / I2P no Chave de configuração
tub.location). Isso evita que os clientes mal configurados sejam Desingonizando-se acidentalmente, conectando-se ao seu servidor através de A Internet rastreável.Claramente, um servidor que está disponível como um serviço Tor / I2P * e * a O endereço TCP regular não é anônimo: o endereço do .on e o real O endereço IP do servidor é facilmente vinculável.
Além disso, a interação, através do Tor, com um Tor Oculto pode ser mais Protegido da análise do tráfego da rede do que a interação, através do Tor, Com um servidor TCP / IP com rastreamento público
** XXX há um documento mantido pelos desenvolvedores de Tor que comprovem ou refutam essa crença? Se assim for, precisamos ligar a ele. Caso contrário, talvez devêssemos explicar mais aqui por que pensamos isso? **
Linkability
A partir de 1.12.0, o nó usa uma única chave de banheira persistente para saída Conexões ao Introdutor e conexões de entrada para o Servidor de Armazenamento (E Helper). Para os clientes, uma nova chave Tub é criada para cada servidor de armazenamento Nós aprendemos sobre, e essas chaves são * não * persistiram (então elas mudarão cada uma delas Tempo que o cliente reinicia).
Clientes que atravessam diretórios (de rootcap para subdiretório para filecap) são É provável que solicitem os mesmos índices de armazenamento (SIs) na mesma ordem de cada vez. Um cliente conectado a vários servidores irá pedir-lhes todos para o mesmo SI em Quase ao mesmo tempo. E dois clientes que compartilham arquivos ou diretórios Irá visitar os mesmos SI (em várias ocasiões).
Como resultado, as seguintes coisas são vinculáveis, mesmo com
revelar-endereço IP = Falso:- Servidores de armazenamento podem vincular reconhecer várias conexões do mesmo Cliente ainda não reiniciado. (Observe que o próximo recurso de Contabilidade pode Faz com que os clientes apresentem uma chave pública persistente do lado do cliente quando Conexão, que será uma ligação muito mais forte).
- Os servidores de armazenamento provavelmente podem deduzir qual cliente está acessando dados, por Olhando as SIs sendo solicitadas. Vários servidores podem conciliar Determine que o mesmo cliente está falando com todos eles, mesmo que o TubIDs são diferentes para cada conexão.
- Os servidores de armazenamento podem deduzir quando dois clientes diferentes estão compartilhando dados.
- O Introdutor pode entregar diferentes informações de servidor para cada um Cliente subscrito, para particionar clientes em conjuntos distintos de acordo com Quais as conexões do servidor que eles eventualmente fazem. Para clientes + nós de servidor, ele Também pode correlacionar o anúncio do servidor com o cliente deduzido identidade.
atuação
Um cliente que se conecta a um servidor Tahoe-LAFS com rastreamento público através de Tor Incorrem em latência substancialmente maior e, às vezes, pior Mesmo cliente se conectando ao mesmo servidor através de um TCP / IP rastreável normal conexão. Quando o servidor está em um Tor Hidden Service, ele incorre ainda mais Latência e, possivelmente, ainda pior rendimento.
Conectando-se a servidores Tahoe-LAFS que são servidores I2P incorrem em maior latência E pior rendimento também.
Efeitos positivos e negativos em outros usuários Tor
O envio de seu tráfego Tahoe-LAFS sobre o Tor adiciona tráfego de cobertura para outros Tor usuários que também estão transmitindo dados em massa. Então isso é bom para Eles - aumentando seu anonimato.
No entanto, torna o desempenho de outros usuários do Tor Sessões - por exemplo, sessões ssh - muito pior. Isso é porque Tor Atualmente não possui nenhuma prioridade ou qualidade de serviço Recursos, para que as teclas de Ssh de outra pessoa possam ter que esperar na fila Enquanto o conteúdo do arquivo em massa é transmitido. O atraso adicional pode Tornar as sessões interativas de outras pessoas inutilizáveis.
Ambos os efeitos são duplicados se você carregar ou baixar arquivos para um Tor Hidden Service, em comparação com se você carregar ou baixar arquivos Over Tor para um servidor TCP / IP com rastreamento público
Efeitos positivos e negativos em outros usuários do I2P
Enviar seu tráfego Tahoe-LAFS ao I2P adiciona tráfego de cobertura para outros usuários do I2P Que também estão transmitindo dados. Então, isso é bom para eles - aumentando sua anonimato. Não prejudicará diretamente o desempenho de outros usuários do I2P Sessões interativas, porque a rede I2P possui vários controles de congestionamento e Recursos de qualidade de serviço, como priorizar pacotes menores.
No entanto, se muitos usuários estão enviando tráfego Tahoe-LAFS ao I2P e não tiverem Seus roteadores I2P configurados para participar de muito tráfego, então o I2P A rede como um todo sofrerá degradação. Cada roteador Tahoe-LAFS que usa o I2P tem Seus próprios túneis de anonimato que seus dados são enviados. Em média, um O nó Tahoe-LAFS requer 12 outros roteadores I2P para participar de seus túneis.
Portanto, é importante que o seu roteador I2P esteja compartilhando a largura de banda com outros Roteadores, para que você possa retornar enquanto usa o I2P. Isso nunca prejudicará a Desempenho de seu nó Tahoe-LAFS, porque seu roteador I2P sempre Priorize seu próprio tráfego.
=========================
Como configurar um servidor
Muitos nós Tahoe-LAFS são executados como "servidores", o que significa que eles fornecem serviços para Outras máquinas (isto é, "clientes"). Os dois tipos mais importantes são os Introdução e Servidores de armazenamento.
Para ser útil, os servidores devem ser alcançados pelos clientes. Os servidores Tahoe podem ouvir Em portas TCP e anunciar sua "localização" (nome do host e número da porta TCP) Para que os clientes possam se conectar a eles. Eles também podem ouvir os serviços de cebola "Tor" E portas I2P.
Os servidores de armazenamento anunciam sua localização ao anunciá-lo ao Introdutivo, Que então transmite a localização para todos os clientes. Então, uma vez que a localização é Determinado, você não precisa fazer nada de especial para entregá-lo.
O próprio apresentador possui uma localização, que deve ser entregue manualmente a todos Servidores de armazenamento e clientes. Você pode enviá-lo para os novos membros do seu grade. Esta localização (juntamente com outros identificadores criptográficos importantes) é Escrito em um arquivo chamado
private / introducer.furlno Presenter's Diretório básico, e deve ser fornecido como o argumento--introducer =paraTahoe create-nodeoutahoe create-node.O primeiro passo ao configurar um servidor é descobrir como os clientes irão alcançar. Então você precisa configurar o servidor para ouvir em algumas portas, e Depois configure a localização corretamente.
Configuração manual
Cada servidor tem duas configurações em seu arquivo
tahoe.cfg:tub.port, eTub.location. A "porta" controla o que o nó do servidor escuta: isto Geralmente é uma porta TCP.A "localização" controla o que é anunciado para o mundo exterior. Isto é um "Sugestão de conexão foolscap", e inclui tanto o tipo de conexão (Tcp, tor ou i2p) e os detalhes da conexão (nome do host / endereço, porta número). Vários proxies, gateways e redes de privacidade podem ser Envolvido, então não é incomum para
tub.portetub.locationpara olhar diferente.Você pode controlar diretamente a configuração
tub.portetub.locationConfigurações, fornecendo--port =e--location =ao executartahoe Create-node.Configuração automática
Em vez de fornecer
--port = / - location =, você pode usar--listen =. Os servidores podem ouvir em TCP, Tor, I2P, uma combinação desses ou nenhum. O argumento--listen =controla quais tipos de ouvintes o novo servidor usará.--listen = nonesignifica que o servidor não deve ouvir nada. Isso não Faz sentido para um servidor, mas é apropriado para um nó somente cliente. o O comandotahoe create-clientinclui automaticamente--listen = none.--listen = tcpé o padrão e liga uma porta de escuta TCP padrão. Usar--listen = tcprequer um argumento--hostname =também, que será Incorporado no local anunciado do nó. Descobrimos que os computadores Não pode determinar de forma confiável seu nome de host acessível externamente, então, em vez de Ter o servidor adivinhar (ou escanear suas interfaces para endereços IP Isso pode ou não ser apropriado), a criação de nó requer que o usuário Forneça o nome do host.--listen = torconversará com um daemon Tor local e criará uma nova "cebola" Servidor "(que se parece comalzrgrdvxct6c63z.onion).--listen = i2p` conversará com um daemon I2P local e criará um novo servidor endereço. Consulte: doc:anonymity-configuration` para obter detalhes.Você pode ouvir nos três usando
--listen = tcp, tor, i2p.Cenários de implantação
A seguir, alguns cenários sugeridos para configurar servidores usando Vários transportes de rede. Estes exemplos não incluem a especificação de um Apresentador FURL que normalmente você gostaria quando provisionamento de armazenamento Nós. Para estes e outros detalhes de configuração, consulte : Doc:
configuration.. `Servidor possui um nome DNS público '
.
Servidor possui um endereço público IPv4 / IPv6_.
O servidor está por trás de um firewall com encaminhamento de porta_.
Usando o I2P / Tor para evitar o encaminhamento da porta_O servidor possui um nome DNS público
O caso mais simples é o local onde o host do servidor está diretamente conectado ao Internet, sem um firewall ou caixa NAT no caminho. A maioria dos VPS (Virtual Private Servidor) e servidores colocados são assim, embora alguns fornecedores bloqueiem Muitas portas de entrada por padrão.
Para esses servidores, tudo o que você precisa saber é o nome do host externo. O sistema O administrador irá dizer-lhe isso. O principal requisito é que este nome de host Pode ser pesquisado no DNS, e ele será mapeado para um endereço IPv4 ou IPv6 que Alcançará a máquina.
Se o seu nome de host for
example.net, então você criará o introdutor como esta::Tahoe create-introducer --hostname example.com ~ / introducer
Ou um servidor de armazenamento como ::
Tahoe create-node --hostname = example.net
Estes irão alocar uma porta TCP (por exemplo, 12345), atribuir
tub.portpara serTcp: 12345etub.locationserãotcp: example.com: 12345.Idealmente, isso também deveria funcionar para hosts compatíveis com IPv6 (onde o nome DNS Fornece um registro "AAAA", ou ambos "A" e "AAAA"). No entanto Tahoe-LAFS O suporte para IPv6 é novo e ainda pode ter problemas. Por favor, veja o ingresso
# 867_ para detalhes... _ # 867: https://tahoe-lafs.org/trac/tahoe-lafs/ticket/867
O servidor possui um endereço público IPv4 / IPv6
Se o host tiver um endereço IPv4 (público) rotativo (por exemplo,
203.0.113.1```), mas Nenhum nome DNS, você precisará escolher uma porta TCP (por exemplo,3457``) e usar o Segue::Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 3457
--porté uma "string de especificação de ponto de extremidade" que controla quais locais Porta em que o nó escuta.--locationé a "sugestão de conexão" que ele Anuncia para outros, e descreve as conexões de saída que essas Os clientes irão fazer, por isso precisa trabalhar a partir da sua localização na rede.Os nós Tahoe-LAFS escutam em todas as interfaces por padrão. Quando o host é Multi-homed, você pode querer fazer a ligação de escuta ligar apenas a uma Interface específica, adicionando uma opção
interface =ao--port =argumento::Tahoe create-node --port = tcp: 3457: interface = 203.0.113.1 - localização = tcp: 203.0.113.1: 3457
Se o endereço público do host for IPv6 em vez de IPv4, use colchetes para Envolva o endereço e altere o tipo de nó de extremidade para
tcp6::Tahoe create-node --port = tcp6: 3457 - localização = tcp: [2001: db8 :: 1]: 3457
Você pode usar
interface =para vincular a uma interface IPv6 específica também, no entanto Você deve fazer uma barra invertida - escapar dos dois pontos, porque, de outra forma, eles são interpretados Como delimitadores pelo idioma de especificação do "ponto final" torcido. o--location =argumento não precisa de dois pontos para serem escapados, porque eles são Envolto pelos colchetes ::Tahoe create-node --port = tcp6: 3457: interface = 2001 \: db8 \: \: 1 --location = tcp: [2001: db8 :: 1]: 3457
Para hosts somente IPv6 com registros DNS AAAA, se o simples
--hostname =A configuração não funciona, eles podem ser informados para ouvir especificamente Porta compatível com IPv6 com este ::Tahoe create-node --port = tcp6: 3457 - localização = tcp: example.net: 3457
O servidor está por trás de um firewall com encaminhamento de porta
Para configurar um nó de armazenamento por trás de um firewall com encaminhamento de porta, você irá precisa saber:
- Endereço IPv4 público do roteador
- A porta TCP que está disponível de fora da sua rede
- A porta TCP que é o destino de encaminhamento
- Endereço IPv4 interno do nó de armazenamento (o nó de armazenamento em si é
Desconhece esse endereço e não é usado durante
tahoe create-node, Mas o firewall deve ser configurado para enviar conexões para isso)
Os números de porta TCP internos e externos podem ser iguais ou diferentes Dependendo de como o encaminhamento da porta está configurado. Se é mapear portas 1-para-1, eo endereço IPv4 público do firewall é 203.0.113.1 (e Talvez o endereço IPv4 interno do nó de armazenamento seja 192.168.1.5), então Use um comando CLI como este ::
Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 3457
Se no entanto, o firewall / NAT-box encaminha a porta externa * 6656 * para o interno Porta 3457, então faça isso ::
Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 6656
Usando o I2P / Tor para evitar o encaminhamento da porta
Os serviços de cebola I2P e Tor, entre outras excelentes propriedades, também fornecem NAT Penetração sem encaminhamento de porta, nomes de host ou endereços IP. Então, configurando Um servidor que escuta apenas no Tor é simples ::
Tahoe create-node --listen = tor
Para mais informações sobre o uso de Tahoe-LAFS com I2p e Tor veja : Doc:
anonymity-configuration -
 @ 75c02714:0e216b7e
2025-04-18 17:57:55
@ 75c02714:0e216b7e
2025-04-18 17:57:55QH99 nổi bật như một hệ sinh thái kỹ thuật số được thiết kế tinh tế nhằm mang lại trải nghiệm mượt mà, hiệu quả và mang tính cá nhân hóa cao cho người dùng trong thời đại số. Với một giao diện thân thiện và bố cục thông minh, nền tảng giúp người dùng dễ dàng tiếp cận các tính năng quan trọng mà không cần mất thời gian làm quen. Khả năng tương thích linh hoạt trên nhiều thiết bị — từ điện thoại thông minh, máy tính bảng đến máy tính để bàn — giúp người dùng có thể truy cập mọi lúc, mọi nơi mà không bị gián đoạn hay thay đổi trải nghiệm. Điều đặc biệt là QH99 liên tục cải tiến công nghệ giao diện dựa trên phản hồi thực tế từ cộng đồng người dùng, từ đó tối ưu hóa các nút chức năng, tốc độ tải trang và khả năng hiển thị nội dung sao cho vừa đẹp mắt vừa dễ sử dụng. Nhờ vậy, mỗi lần truy cập vào QH99 luôn mang đến cảm giác mới mẻ nhưng vẫn quen thuộc, cho phép người dùng thao tác nhanh gọn, tiết kiệm thời gian và tăng cường sự tập trung vào mục tiêu chính.
Không chỉ chú trọng đến trải nghiệm người dùng, QH99 còn đầu tư sâu vào nền tảng công nghệ và bảo mật dữ liệu. Mọi thao tác và luồng thông tin đều được xử lý qua các lớp mã hóa hiện đại, đảm bảo tuyệt đối về quyền riêng tư và tính an toàn trong mọi tình huống. Hệ thống được xây dựng dựa trên cấu trúc máy chủ hiệu năng cao, có khả năng xử lý lưu lượng truy cập lớn một cách trơn tru và nhanh chóng. Ngoài ra, QH99 còn tích hợp các thuật toán thông minh giúp tự động phát hiện và ngăn chặn các hành vi bất thường, từ đó giảm thiểu rủi ro và duy trì trạng thái ổn định cho toàn bộ nền tảng. Những cơ chế phòng ngừa này không chỉ mang tính kỹ thuật mà còn được hỗ trợ bởi đội ngũ chuyên môn túc trực liên tục nhằm theo dõi, nâng cấp và tối ưu hệ thống theo thời gian thực. Sự đầu tư bài bản vào bảo mật và vận hành như vậy chính là yếu tố nền tảng giúp QH99 xây dựng được niềm tin lâu dài từ cộng đồng người dùng rộng lớn.
Hơn cả một nền tảng công nghệ thông minh, QH99 còn đóng vai trò như một người đồng hành đáng tin cậy trong hành trình số hóa cá nhân của mỗi người dùng. Với định hướng phát triển bền vững và tầm nhìn chiến lược rõ ràng, QH99 không ngừng cập nhật những xu hướng công nghệ mới nhất, từ trí tuệ nhân tạo, học máy đến phân tích dữ liệu lớn để mang lại những giá trị thiết thực trong từng tương tác. Hệ thống liên tục học hỏi từ thói quen và nhu cầu của người dùng, từ đó đưa ra những đề xuất thông minh, giúp cá nhân hóa trải nghiệm ở mức độ sâu hơn. Đây chính là sự khác biệt khiến QH99 trở thành một nền tảng không chỉ phục vụ mà còn hiểu và phát triển cùng người dùng. Trong bối cảnh công nghệ ngày càng bùng nổ, QH99 đang chứng tỏ rằng mình không chỉ theo kịp xu thế mà còn tiên phong tạo ra chuẩn mực mới cho sự kết nối và trải nghiệm số hiện đại.
-
 @ 3f770d65:7a745b24
2025-01-19 21:48:49
@ 3f770d65:7a745b24
2025-01-19 21:48:49The recent shutdown of TikTok in the United States due to a potential government ban serves as a stark reminder how fragile centralized platforms truly are under the surface. While these platforms offer convenience, a more polished user experience, and connectivity, they are ultimately beholden to governments, corporations, and other authorities. This makes them vulnerable to censorship, regulation, and outright bans. In contrast, Nostr represents a shift in how we approach online communication and content sharing. Built on the principles of decentralization and user choice, Nostr cannot be banned, because it is not a platform—it is a protocol.
PROTOCOLS, NOT PLATFORMS.
At the heart of Nostr's philosophy is user choice, a feature that fundamentally sets it apart from legacy platforms. In centralized systems, the user experience is dictated by a single person or governing entity. If the platform decides to filter, censor, or ban specific users or content, individuals are left with little action to rectify the situation. They must either accept the changes or abandon the platform entirely, often at the cost of losing their social connections, their data, and their identity.
What's happening with TikTok could never happen on Nostr. With Nostr, the dynamics are completely different. Because it is a protocol, not a platform, no single entity controls the ecosystem. Instead, the protocol enables a network of applications and relays that users can freely choose from. If a particular application or relay implements policies that a user disagrees with, such as censorship, filtering, or even government enforced banning, they are not trapped or abandoned. They have the freedom to move to another application or relay with minimal effort.
THIS IS POWERFUL.
Take, for example, the case of a relay that decides to censor specific content. On a legacy platform, this would result in frustration and a loss of access for users. On Nostr, however, users can simply connect to a different relay that does not impose such restrictions. Similarly, if an application introduces features or policies that users dislike, they can migrate to a different application that better suits their preferences, all while retaining their identity and social connections.
The same principles apply to government bans and censorship. A government can ban a specific application or even multiple applications, just as it can block one relay or several relays. China has implemented both tactics, yet Chinese users continue to exist and actively participate on Nostr, demonstrating Nostr's ability to resistant censorship.
How? Simply, it turns into a game of whack-a-mole. When one relay is censored, another quickly takes its place. When one application is banned, another emerges. Users can also bypass these obstacles by running their own relays and applications directly from their homes or personal devices, eliminating reliance on larger entities or organizations and ensuring continuous access.
AGAIN, THIS IS POWERUFL.
Nostr's open and decentralized design makes it resistant to the kinds of government intervention that led to TikTok's outages this weekend and potential future ban in the next 90 days. There is no central server to target, no company to regulate, and no single point of failure. (Insert your CEO jokes here). As long as there are individuals running relays and applications, users continue creating notes and sending zaps.
Platforms like TikTok can be silenced with the stroke of a pen, leaving millions of users disconnected and abandoned. Social communication should not be silenced so incredibly easily. No one should have that much power over social interactions.
Will we on-board a massive wave of TikTokers in the coming hours or days? I don't know.
TikTokers may not be ready for Nostr yet, and honestly, Nostr may not be ready for them either. The ecosystem still lacks the completely polished applications, tools, and services they’re accustomed to. This is where we say "we're still early". They may not be early adopters like the current Nostr user base. Until we bridge that gap, they’ll likely move to the next centralized platform, only to face another government ban or round of censorship in the future. But eventually, there will come a tipping point, a moment when they’ve had enough. When that time comes, I hope we’re prepared. If we’re not, we risk missing a tremendous opportunity to onboard people who genuinely need Nostr’s freedom.
Until then, to all of the Nostr developers out there, keep up the great work and keep building. Your hard work and determination is needed.
-
 @ 75c02714:0e216b7e
2025-04-18 17:57:11
@ 75c02714:0e216b7e
2025-04-18 17:57:11MU8 được thiết kế như một nền tảng công nghệ mang tính đột phá, nơi mọi trải nghiệm của người dùng được cá nhân hóa và tối ưu hóa đến từng chi tiết nhỏ nhất. Với mục tiêu mang lại sự tiện lợi và linh hoạt tối đa, MU8 không ngừng hoàn thiện giao diện người dùng, tập trung vào tốc độ truy cập, độ phản hồi cao và khả năng thích ứng với đa dạng thiết bị. Người dùng có thể dễ dàng thao tác trên điện thoại di động, máy tính bảng hay máy tính để bàn mà không gặp phải sự gián đoạn nào trong quá trình sử dụng. Bố cục giao diện được bố trí trực quan, màu sắc hài hòa và nút chức năng rõ ràng giúp người dùng dễ dàng điều hướng và tìm thấy thông tin một cách nhanh chóng. Hơn nữa, hệ thống được lập trình để ghi nhớ các hành vi sử dụng quen thuộc của từng người dùng, từ đó đề xuất những tùy chọn phù hợp, góp phần rút ngắn thời gian thao tác và nâng cao hiệu suất trải nghiệm tổng thể.
MU8 cũng đặc biệt chú trọng đến vấn đề an toàn thông tin và độ ổn định của nền tảng — hai yếu tố then chốt làm nên uy tín trong môi trường số hiện đại. Mọi dữ liệu và thông tin cá nhân đều được xử lý qua hệ thống mã hóa đa lớp, đảm bảo không thể bị truy cập trái phép hoặc thất thoát trong bất kỳ tình huống nào. Nền tảng được xây dựng trên hạ tầng máy chủ hiện đại, kết hợp với các thuật toán giám sát hoạt động thông minh nhằm nhanh chóng phát hiện và xử lý các rủi ro tiềm ẩn trước khi chúng ảnh hưởng đến người dùng. Điều này tạo nên một hệ thống vận hành ổn định, tin cậy, giúp người dùng yên tâm sử dụng các tính năng trong suốt thời gian dài mà không gặp trở ngại kỹ thuật. Bên cạnh đó, đội ngũ hỗ trợ kỹ thuật luôn túc trực 24/7 để giải đáp mọi thắc mắc và xử lý sự cố một cách nhanh chóng, đảm bảo người dùng luôn cảm nhận được sự đồng hành chuyên nghiệp và chu đáo.
Ngoài những ưu điểm vượt trội về mặt kỹ thuật và bảo mật, MU8 còn nổi bật nhờ khả năng liên tục cập nhật và nâng cấp để đáp ứng nhu cầu ngày càng cao của người dùng trong thời đại công nghệ phát triển không ngừng. Mỗi lần cập nhật đều được thực hiện dựa trên những phản hồi thực tế từ cộng đồng sử dụng, đảm bảo rằng mọi cải tiến đều mang lại giá trị thiết thực, từ tính năng mới cho đến trải nghiệm người dùng mượt mà hơn. Hệ thống đề xuất thông minh, tùy chỉnh giao diện theo sở thích cá nhân và khả năng tích hợp công nghệ mới như AI hay dữ liệu lớn chính là minh chứng cho định hướng phát triển lâu dài của MU8. Trong tương lai gần, MU8 không chỉ là nền tảng số mạnh mẽ mà còn là người bạn đồng hành đáng tin cậy, giúp người dùng hiện đại chủ động hơn trong việc tiếp cận công nghệ và khai thác tối đa tiềm năng từ không gian kỹ thuật số ngày càng đa chiều.
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ f1989a96:bcaaf2c1
2025-03-27 13:53:14
@ f1989a96:bcaaf2c1
2025-03-27 13:53:14Good morning, readers!
Turkey’s currency plunged to a record low after the arrest of Istanbul Mayor Ekrem Imamoglu, one of President Recep Tayyip Erdogan’s main political rivals. This follows a pattern of escalating repression of opposition figures, which have been described as an effort to suppress competition ahead of primary elections. As economic conditions deteriorate, Erdogan is resorting to desperate measures — blocking social media, arresting dissenters, and tear-gassing protests — to maintain power over an increasingly restless populace.
In the Caribbean, we shed light on Cubans' struggles accessing remittances sent from family members abroad. This is a symptom of the regime's strict monetary controls over foreign currency. Cubans face long delays or can’t withdraw cash due to bank liquidity shortages. And when they can, remittances are converted into pesos at the overvalued official Cuban exchange rate. This effectively allows the Communist Party of Cuba (PCC) to loot the value from Cuban remittances.
In freedom tech news, we highlight Demand Pool, the first-ever Stratum V2 mining pool. Stratum V2 is a mining protocol designed to decentralize Bitcoin mining by letting individual miners create their own block templates rather than relying on centralized pools to do so for them. This improves censorship resistance and promotes a more decentralized and resilient Bitcoin network — critical features for human rights defenders and nonprofits using Bitcoin to protect against financial repression from authoritarian regimes.
We end by featuring Vijay Selvam's new book, “Principles of Bitcoin.” It offers a clear, first-principles guide to understanding how Bitcoin’s technology interacts with economics, politics, philosophy, and human rights. Whether you’re new to Bitcoin or looking to deepen your understanding, this book provides a solid foundation, and it even features a foreword by HRF Chief Strategy Officer Alex Gladstein.
Now, let’s dive right in!
Subscribe Here
GLOBAL NEWS
Turkey | Lira in Free Fall as Erdogan Arrests Political Rival
Turkey’s lira plunged to a record low after officials arrested Istanbul Mayor Ekrem Imamoglu, President Recep Tayyip Erdogan’s main political rival. Imamoglu’s arrest comes ahead of primary elections and follows the increasing repression of opposition figures in recent months, including the suspension of political opposition accounts on X. Officials also arrested Buğra Gökçe, head of the Istanbul Planning Agency, for publishing data exposing the country’s deepening poverty. The currency’s fallout and political repression have sparked protests in Istanbul despite a four-day ban. The regime is responding with tear gas and rubber bullets. Meanwhile, Turks dissenting online risk joining over a dozen other citizens recently arrested for “provocative” social media posts. Netblocks reports that the Turkish regime imposed restrictions on social media and messaging to quell the uprising of Turks struggling with financial conditions and deepening repression.
Cuba | Banks “Hijack” Citizen Remittances
Cubans are struggling to access remittances sent from their families abroad. This is because the regime completely controls all incoming foreign currency transfers. When remittances arrive, communist banking authorities force their conversion into collapsing Cuban pesos or “Moneda Libremente Convertible” (MLC), Cuba’s digital currency with limited use. On top of this, Cubans receive pesos in their accounts based on the official Cuban exchange rate, which is far below the informal market rate. This allows the regime to opaquely siphon off much of the remittances’ real value. Even when the money clears, Cubans face long delays or can’t withdraw the cash due to banks’ liquidity shortages. Many Cubans are accusing these banks of “hijacking” their remittances. As inflation, electrical blackouts, and food shortages continue, remittances are more critical than ever for Cuban families. Yet, they’re blocked at every turn by a system designed to impoverish them.
Pakistan | Announces Plans to Regulate Digital Assets
Pakistan announced plans to create a regulatory framework for Bitcoin and digital assets to attract foreign investment and domestic economic activity. It’s a peculiar shift for a regime that regularly suspends the Internet, censors social media, represses opposition, and burdens its people with the highest cost of living in Asia. We suspect the plans indicate efforts to control the industry rather than empower individuals. The military-backed regime is also exploring a Central Bank Digital Currency (CBDC) and tightening controls on VPN use, which are hardly the hallmarks of leadership committed to permissionless financial systems. But perhaps it matters little. Grassroots Bitcoin adoption in Pakistan already ranks among the highest in the world, with an estimated 15 to 20 million users turning to digital assets to preserve their savings, circumvent financial controls, and escape the failures of a collapsing fiat system. HRF supported Bitcoin Pakistan with a grant to help translate resources into Urdu, a language spoken by 60 million people trapped in this repressive scenario.
Russia | Piloting CBDC in Tatarstan to Test Smart Contract Functionality
Russia’s central bank plans to pilot its CBDC, the digital ruble, in Tatarstan to test smart contract functionality. Specifically, the central bank will experiment with conditional spending, using smart contracts to restrict where and what users can spend money on. If these features are implemented, it will empower the Kremlin with micro-controls over Russians’ spending activity. Officials could program funds to expire, restrict purchases to regime-approved goods, or block transactions at certain locations — leaving users with no financial autonomy or privacy. Those who oppose the Russian dictatorship, such as activists, nonprofits, and dissenters, could be debanked with more ease, their assets frozen or confiscated without recourse.
Nicaragua | Government Mandates Public Employees Declare All Assets
In Nicaragua, dictator Daniel Ortega intensified state financial surveillance by mandating all public servants to disclose information on all personal and family assets. The mandate requires all public employees to declare everything from personal bank accounts, loans, vehicles, and other assets — as well as the assets and accounts of immediate family members. Those who do not comply face the threat of termination. Ironically, despite the law requiring such disclosure, Ortega himself has not declared his assets since 2006. Under the guise of regulatory compliance, this policy is yet another link in the chain tightening state surveillance over Nicaraguan society. Bitcoin adoption continues to grow in this repressed Central American nation.
BITCOIN AND FREEDOM TECH NEWS
Demand Pool | First Stratum V2 Mining Pool Launches
Bitcoin mining could become more decentralized and censorship-resistant with the launch of Demand Pool, the first mining pool to ever implement Stratum V2. Stratum V2 is open-source software that allows miners to build their own block templates, enabling more individual mining and less dependence on large and centralized mining pools. This helps maintain Bitcoin’s key features: its decentralized, permissionless, and uncensorable nature. All of which are crucial for human rights defenders and nonprofits bypassing the financial repression and surveillance of authoritarian regimes. Learn more here.
Bitcoin Mining | Three Solo Blocks Found
Three separate solo miners mined Bitcoin blocks in the past seven days. This marks the second, third, and fourth solo blocks mined in the past two weeks alone, hinting at a surge in home mining. This promotes greater decentralization within the Bitcoin network because solo miners have little functional ability to censor. In contrast, large mining pools are points of failure that centralized interests can more easily pressure — to the detriment of activists and human rights defenders. The first block was mined on March 21 by a miner using a self-hosted FutureBit Apollo machine that earned 3.125 BTC plus fees for processing block 888,737. Just days later, a solo miner with under 1 TH/s of self-hosted hash rate found block 888,989, which became just the third block ever to be mined using an open-source Bitaxe device. Most recently, on March 24, a solo miner using a $300 setup successfully mined block 889,240.
Krux | Adds Taproot and Miniscript Support
Krux, open-source software for building your own Bitcoin signing devices (hardware for Bitcoin self-custody), released an update that enhances privacy and flexibility. The update introduces support for Taproot, a past Bitcoin upgrade that improves privacy and security, and Miniscript, a simplified way to create more complex Bitcoin transaction rules. This allows users to manage multi-signature wallets (where more than one private key is required to interact with your Bitcoin) in a more private and flexible way. It also enables spending conditions that are harder to censor and easier to verify. Krux continues to support the struggle for financial freedom and human rights by breaking down barriers to Bitcoin self-custody. HRF has recognized this impact and awarded grants to open-source developers working on Krux to advance this mission.
Cashu | Developing Tap-to-Pay Ecash
Calle, the creator of Cashu, an open-source Chaumian ecash protocol for Bitcoin integrated with the Lightning Network, is developing a new tap-to-pay feature that enables instant, offline ecash payments via NFC. Ecash functions as a bearer asset, meaning the funds are stored directly on the user’s device. With tap-to-pay, it can be transferred with a single tap (similar to tapping your credit card). More generally, ecash offers fast, private transactions resistant to surveillance and censorship. But for activists and dissenters, this particular advancement makes private and permissionless payments more accessible and user-friendly. This development will be worth following closely. Watch a demo here.
OpenSats | Announces 10th Wave of Bitcoin Grants
OpenSats, a public nonprofit that supports open-source software and projects, announced its 10th wave of grants supporting Bitcoin initiatives. This round includes funding for Stable Channels, which enable stabilized Bitcoin-backed balances on the Lightning Network (allowing users to peg Bitcoin to fiat currencies in a self-custodial way) that provide stable, censorship-resistant payments. OpenSats also renewed its support for Floresta, a lightweight Bitcoin node (a computer that runs the Bitcoin software). It lowers entry barriers to running Bitcoin, helping make the network more decentralized and censorship-resistant.
Bitcoin Policy Institute | Launches Bitcoin Summer Research Program
The Bitcoin Student Network (BSN) and the Bitcoin Policy Institute (BPI) are teaming up to offer students an eight-week research internship this summer. The program is part of BPI’s Research Experiences for Undergraduates (REU) initiative and invites students passionate about the future of money, financial inclusion, and Bitcoin’s civil liberties impacts to conduct hands-on research. Participants will also receive mentorship from BPI researchers. The program runs from June 9 to Aug. 8, 2025, and includes an in-person colloquium in Washington, DC. It is an incredible opportunity for students worldwide, especially those living in oppressive regimes, to get involved with Bitcoin. Applications are open until April 7. Apply here.
RECOMMENDED CONTENT
Principles of Bitcoin by Vijay Selvam
“Principles of Bitcoin” by Vijay Selvam is a new book offering a first-principles guide to understanding Bitcoin’s technology, economics, politics, and philosophy. With a foreword by HRF Chief Strategy Officer Alex Gladstein, the book cuts through the noise to explain why Bitcoin stands alone as a tool for individual empowerment and financial freedom. Selvam’s work makes the case for Bitcoin as a once-in-history invention shaping a more decentralized and equitable future. Read it here.
Rule Breakers — The True Story of Roya Mahboob
“Rule Breakers” is a new film that tells the true story of Roya Mahboob, Afghanistan’s first female tech CEO, who empowered young girls in Afghanistan with financial literacy, robotics, and financial freedom through Bitcoin. The film recounts Mahboob’s courageous work educating these girls despite huge personal risks under a regime that bans their education. It follows the story of Afghan Dreamers, the country’s first all-girls robotics team, and the obstacles they overcome to compete on the world stage. “Rule Breakers” is a testament to the power of education, innovation, and resilience in the face of oppression. It’s now in theaters, and you can watch the trailer here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 75c02714:0e216b7e
2025-04-18 17:55:51
@ 75c02714:0e216b7e
2025-04-18 17:55:51BL555 không chỉ đơn thuần là một nền tảng số với giao diện thân thiện và dễ sử dụng, mà còn là sự kết tinh của tư duy thiết kế hiện đại và công nghệ vận hành mạnh mẽ, phục vụ nhu cầu ngày càng cao và đa dạng của người dùng. Với mục tiêu tối ưu hóa trải nghiệm trong từng chi tiết, BL555 đã áp dụng những xu hướng giao diện mới nhất để đảm bảo mọi thao tác đều trực quan và mượt mà, bất kể người dùng đang sử dụng thiết bị nào. Giao diện của nền tảng này được sắp xếp hợp lý, dễ nắm bắt và tối ưu hóa khả năng phản hồi, giúp người dùng thao tác nhanh chóng, không bị rối mắt hay phải mất thời gian tìm kiếm thông tin cần thiết. Hệ thống menu được bố trí gọn gàng, tích hợp các tính năng hỗ trợ nhanh như tìm kiếm tức thời, điều hướng thông minh và phản hồi trực tiếp, tạo nên một không gian công nghệ thân thiện, phục vụ mọi đối tượng người dùng dù là mới làm quen hay đã quen thuộc với nền tảng số.
Yếu tố làm nên sự khác biệt nổi bật của BL555 chính là khả năng vận hành ổn định và mức độ an toàn được đầu tư nghiêm túc. BL555 xây dựng hệ thống dựa trên nền tảng công nghệ tiên tiến, ứng dụng các phương thức bảo mật đa tầng để đảm bảo an toàn tuyệt đối cho người dùng. Tất cả dữ liệu cá nhân và thông tin hoạt động đều được mã hóa theo chuẩn quốc tế, giúp ngăn ngừa tối đa nguy cơ bị đánh cắp hoặc rò rỉ thông tin. Hệ thống còn tích hợp các công cụ giám sát hoạt động 24/7, liên tục theo dõi hiệu năng cũng như khả năng phát hiện các hành vi bất thường. Khi có sự cố kỹ thuật xảy ra, đội ngũ kỹ thuật viên của BL555 sẽ ngay lập tức can thiệp và xử lý nhanh chóng nhằm duy trì sự ổn định cho toàn hệ thống. Sự kết hợp giữa công nghệ hiện đại và con người chuyên nghiệp đã biến BL555 trở thành một nền tảng đáng tin cậy, nơi mà người dùng có thể yên tâm trải nghiệm mà không phải lo lắng về vấn đề bảo mật hay hiệu năng.
Không dừng lại ở việc cung cấp một không gian kỹ thuật số mạnh mẽ, BL555 còn hướng đến việc xây dựng một cộng đồng người dùng bền vững thông qua việc lắng nghe và cải tiến liên tục. Nền tảng luôn chủ động cập nhật các xu hướng công nghệ mới, đồng thời bổ sung các tính năng phù hợp với phản hồi từ người dùng, nhằm đảm bảo rằng mọi cập nhật đều có giá trị thực tế và nâng cao trải nghiệm tổng thể. BL555 hiểu rằng trong thời đại công nghệ phát triển nhanh chóng như hiện nay, yếu tố con người và khả năng thích ứng là hai điểm then chốt quyết định sự thành công lâu dài. Vì vậy, nền tảng không ngừng hoàn thiện từ giao diện đến chức năng, từ dịch vụ hỗ trợ đến bảo mật, để trở thành một điểm đến lý tưởng cho mọi nhu cầu kết nối, sử dụng và phát triển không gian số cá nhân của người dùng. Trong hành trình phía trước, BL555 chắc chắn sẽ tiếp tục khẳng định vị thế của mình bằng chất lượng, sự chuyên nghiệp và tinh thần đổi mới không ngừng.
-
 @ cff1720e:15c7e2b2
2025-01-19 17:48:02
@ cff1720e:15c7e2b2
2025-01-19 17:48:02Einleitung\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie roland@pareto.space können sie sogar jederzeit umziehen, egal wohin. Cool, das ist state of the art! Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.

Warum Nostr?
Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz "unserer Demokratie” praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.

Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ Resümee: keine Standards, keine Daten, keine Rechte = keine Zukunft!

\ Wie funktioniert Nostr?
Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum “single point of failure”, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. roland@pareto.space ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ Resümee: ein offener Standard, alle Daten, alle Rechte = große Zukunft!

\ Warum ist Nostr die Zukunft des Internet?
“Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie (Value4Value). OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.

\ Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.
https://nostr.net/ \ https://start.njump.me/
Hier das Interview zum Thema mit Radio Berliner Morgenröte
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 6b3780ef:221416c8
2025-03-26 18:42:00
@ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments.
Understanding MCP Systems
MCP (Model Context Protocol) systems consist of two main components that work together:
- MCP Server: The heart of the system that exposes tools, which you can access via the
.listTools()method. - MCP Client: The interface that connects to the MCP server and lets you use the tools it offers.
These servers and clients can communicate using different transport methods:
- Standard I/O (stdio): A simple local connection method when your server and client are on the same machine.
- Server-Sent Events (SSE): Uses HTTP to create a communication channel.
For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr.
Creating (or Finding) an MCP Server
Building an MCP server is simpler than you might think:
- Create software in any programming language you're comfortable with.
- Add an MCP library to expose your server's MCP interface.
- Create an API that wraps around your software's functionality.
Once your server is ready, an MCP client can connect, for example, with
bun index.js, and then call.listTools()to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy.Alternatively, you can use one of the many existing MCP servers available in various repositories.
For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/
Setting Up the Workshop
Let's get hands-on:
First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script:
curl -fsSL https://bun.sh/install | bash-
Choose your MCP server: You can either create one or use an existing one.
-
Inspect your server using the MCP inspector tool:
bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2This will: - Launch a client UI (default: http://localhost:5173)
- Start an MCP proxy server (default: port 3000)
-
Pass any additional arguments directly to your server
-
Use the inspector: Open the client UI in your browser to connect with your server, list available tools, and test its functionality.
Deploying with DVMCP
Now for the exciting part – making your MCP server available to everyone on Nostr:
-
Navigate to your MCP server directory.
-
Run without installing (quickest way):
npx @dvmcp/bridge -
Or install globally for regular use:
npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridgeThen run using:bash dvmcp-bridge
This will guide you through creating the necessary configuration.
Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing.
For the configuration, you can set the relay as
wss://relay.dvmcp.fun, or use any other of your preferenceTesting and Integration
- Visit dvmcp.fun to see your DVM announcement.
- Call your tools and watch the responses come back.
For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime.
Integrating with LLM Clients
You can also integrate your DVMCP deployment with LLM clients using the discovery package:
-
Install and use the
@dvmcp/discoverypackage:bash npx @dvmcp/discovery -
This package acts as an MCP server for your LLM system by:
- Connecting to configured Nostr relays
- Discovering tools from DVMCP servers
-
Making them available to your LLM applications
-
Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1...
# Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ```
Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at dvmcp.fun.
This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications.
Final thoughts
If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun.
You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless.
However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr.
Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag.
Useful Resources
- Official Documentation:
- Model Context Protocol: modelcontextprotocol.org
-
DVMCP.fun: dvmcp.fun
-
Source Code and Development:
- DVMCP: github.com/gzuuus/dvmcp
-
DVMCP.fun: github.com/gzuuus/dvmcpfun
-
MCP Servers and Clients:
- Smithery AI: smithery.ai
- MCP.so: mcp.so
-
Glama AI MCP Servers: glama.ai/mcp/servers
Happy building!
- MCP Server: The heart of the system that exposes tools, which you can access via the
-
 @ fd06f542:8d6d54cd
2025-04-15 02:38:14
@ fd06f542:8d6d54cd
2025-04-15 02:38:14排名随机, 列表正在增加中。
Cody Tseng
jumble.social 的作者
https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
- Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
- Building 👨💻:
- https://github.com/CodyTseng/jumble
- https://github.com/CodyTseng/nostr-relay-tray
- https://github.com/CodyTseng/danmakustr
- https://github.com/CodyTseng/nostr-relay-nestjs
- https://github.com/CodyTseng/nostr-relay
- https://github.com/CodyTseng
阿甘
- @agan0
- 0xchat.com
- canidae40@coinos.io
- https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce
joomaen
- Follows you
- joomaen.com
-
95aebd@wallet.yakihonne.com
-
nobot
- https://joomaen.filegear-sg.me/
- https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0
颜值精选官
- wasp@ok0.org
- 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好!
- https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz
6svjszwk
- 6svjszwk@ok0.org
- 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi
-
low-time-preference
-
anarcho-capitalism
-
libertarianism
-
bitcoin #monero
- https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk
𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳
- everyday@iris.to
- 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。
- 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。
- 黑暗森林时代,当好小透明。
- bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww
- https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke
nostr_cn_dev
npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash
Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 * https://www.duozhutuan.com nostrhttp demo * https://github.com/duozhutuan/NostrBridge * * https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm *
CXPLAY
- lightning@cxplay.org
- 😉很高兴遇到你, 你可以叫我 CX 或 CXPLAY, 这个名字没有特殊含义, 无需在意.
- ©本账号下所有内容如未经特殊声明均使用 CC BY-NC-SA 4.0 许可协议授权.
- 🌐如果您在 Fediverse 收到本账号的内容则说明您的实例已与 Mostr.pub 或 Momostr.pink Bridge 互联, 您所看到的账号为镜像, 所有账号内容正在跨网传递. 如有必要请检查原始页面.
- 🧑💻正在提供中文本地化(i10n): #Amethyst #Amber #Citrine #Soapbox #Ditto #Alby
- https://cx.ms/
https://jumble.social/users/npub1gd8e0xfkylc7v8c5a6hkpj4gelwwcy99jt90lqjseqjj2t253s2s6ch58h
w
- 0xchat的作者
- 0xchat@getalby.com
- Building for 0xchat
- https://www.0xchat.com/
- https://jumble.social/users/npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl
Michael
- highman@blink.sv
- Composer Artist | Musician
- 🎹🎼🎤🏸🏝️🐕❤️
- 在這裡可以看到「我看世界」的樣子
- 他是光良
- https://jumble.social/users/npub1kr5vqlelt8l47s2z0l47z4myqg897m04vrnaqks3emwryca3al7sv83ry3
-
 @ 6389be64:ef439d32
2025-01-13 21:50:59
@ 6389be64:ef439d32
2025-01-13 21:50:59Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker
For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper
When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier
The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste
Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste
Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine
Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth
Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones
During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner
Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network
What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain
Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR
The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing
The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data
Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression
Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety
A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap
How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ 4cebd4f5:0ac3ed15
2025-04-18 16:02:42
@ 4cebd4f5:0ac3ed15
2025-04-18 16:02:42Tóm tắt Hackathon BUIDL BATTLE
BUIDL BATTLE | The Bitcoin Builders Tournament kết thúc với 81 dự án được phê duyệt từ 219 developer đăng ký. Sự kiện trực tuyến kéo dài 3 tuần này nhằm thúc đẩy đổi mới trên Bitcoin, mang đến cơ hội tiếp cận cộng đồng builders, nhà đầu tư và accelerator. Trọng tâm xoay quanh các chủ đề Bitcoin DeFi và Real World Utility, với tổng giải thưởng hơn 90.000 USD bao gồm tiền mặt, credit AWS và grants ICP. Những đột phá công nghệ nổi bật ứng dụng Stacks technology và sBTC.
Hackathon chia làm 2 vòng. Các dự án vào chung kết trình bày trước hội đồng giám khảo gồm VC và lãnh đạo ngành để chọn ra quán quân. Người tham gia nhận mentorship và workshop giá trị, đồng thời tăng khả năng gọi vốn ở vòng 2. Sự kiện được hỗ trợ bởi Stacks Foundation, AWS và đối tác, góp phần củng cố hệ sinh thái phát triển Bitcoin.
Các dự án đoạt giải
Bitcoin DeFi 2.0 Prize Winners
Hạng mục tập trung cải thiện scalability, security và user experience cho Bitcoin DeFi.
- BigMarket: Nền tảng prediction market phi tập trung tích hợp AI trên Layer 2 Stacks, vận hành bởi DAO để đưa dự đoán minh bạch.
- BitForward: Platform tạo hợp đồng kỳ hạn (forward contract) dựa trên NFT, xây dựng trên blockchain Stacks của Bitcoin.The 3.0 Digital Economy Prize Winners
Khám phá sự hội tụ của tài chính, giải trí và mạng xã hội trong hệ sinh thái MemeFi, SocialFi, GameFi.
- Kulture.Fun: Nền tảng SocialFi chat phi tập trung với tính năng token-gated và tích hợp Bitcoin.
- Skullcoin: Gamify hóa Bitcoin DeFi thông qua sBTC, kích hoạt thanh khoản BTC trong trò chơi.Real World Ordinals & NFT Usage Prize Winners
Ứng dụng NFT và Ordinals vượt khỏi phạm vi nghệ thuật truyền thống.
- Offers & Counter-offers | BNS One: Marketplace giao dịch tên BNS qua smart contract, loại bỏ trung gian.
- Truth-Chain: Xác minh nguồn gốc và tính xác thực của nội dung số trên nền tảng Stacks.Tooling & Infrastructure Prize Winners
Phát triển công cụ hỗ trợ xây dựng ứng dụng Web3.
- BLAZE PROTOCOL: Layer 2 cải thiện trải nghiệm Web3 với xác nhận giao dịch tức thì.
- PoXAgents: Sử dụng AI agents đơn giản hóa tương tác với Stacks Blockchain cho người dùng phổ thông.ICP Challenge Prize Winners
Tích hợp Internet Computer để giải quyết thách thức blockchain trong hệ sinh thái Bitcoin.
- ckBoost: Tăng tốc giao dịch Bitcoin trên Internet Computer thông qua liquidity pool.
- CounterpartyICP: Module quản lý smart contract và tài sản số trên Bitcoin qua Counterparty API.AWS - Buidl with Bedrock Challenge Prize Winner
Dự án ứng dụng công nghệ AWS.
- Stacks AI: Công cụ AI tạo, debug và học smart contract ngôn ngữ Clarity, sử dụng AWS Bedrock.Xem chi tiết dự án tại Dorahacks.
Về Nhà tổ chức
Stacks Foundation
Stacks Foundation tập trung phát triển Stacks blockchain – Bitcoin Layer 2 hàng đầu, hỗ trợ các dự án tận dụng bảo mật của Bitcoin để xây dựng Internet phi tập trung. Thông qua chương trình Stacks Accelerator, tổ chức đã thúc đẩy đổi mới và thu hút developer cho hệ sinh thái blockchain. Sứ mệnh hiện tại là cung cấp công cụ để phát triển ứng dụng user-owned, củng cố tầm nhìn về web phi tập trung.
-
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.