-
 @ fbe736db:187bb0d5
2025-05-18 14:25:49
@ fbe736db:187bb0d5
2025-05-18 14:25:49This article was published in November 2024 by the Bitcoin Collective and is best viewed here for images
Ssssh. Did you hear that? In their recent Q3 2024 earnings call MicroStrategy (NSQ:MSTR) announced plans to buy a further $42 billion worth of Bitcoin over the next 3 calendar years. Here are some reflections on where MicroStrategy has come from, and where they are going.
From the beginning
Let’s rewind as to how we got here. Microstrategy is a business intelligence software company originally founded by Michael Saylor in 1989.
They started acquiring Bitcoin in Q3 2020, firstly via their cash reserves on the balance sheet. This was soon followed by debt issuance (mainly in the form of convertible debt), and has in more recent years been followed by issuing further MSTR equity into the market, alongside yet more convertible debt issuance.
Nearly all the proceeds have gone towards buying bitcoin. As can be seen on the chart below, they have managed to steadily grow these holdings, albeit this growth visibly slowed in the last bear market.
[p13 of Q3 2024 Earnings Presentation. Please note - all screenshots from this article come from the slide deck accompanying the recent MSTR Q3 earnings presentation, which can be viewed by clicking here]
MSTR now holds well over 1% of all the Bitcoin that will ever exist. With Bitcoin nearing all time highs again, this Bitcoin is worth around $18.3bn at the time of writing, and has an average purchase cost of around $9.9bn.
This has led to a spectacular share price performance, unmatched in the entire S&P 500 since August 2020.
[p23 of Q3 2024 Earnings Presentation]
It was not always this way. When I wrote this article in July 2022, MSTR was firmly in the red and sitting on unrealised bitcoin losses of $1.4bn. A search for Michael Saylor on Twitter back then auto-completed to “Michael Saylor liquidated”.
Rumours of imminent demise were always unfounded since the debt was of long enough term, and with the exception of a small proportion, could not be margin called.
A developing strategy
What’s interesting about MicroStrategy since then is their developing vision as to how to add Bitcoin to their balance sheet and more value to shareholders. This is especially in terms of outperforming BTC and achieving what they define as a “positive BTC yield” – not yield in a conventional sense but a measure of increasing the number of bitcoin held per assumed diluted shares outstanding.
The concept of MSTR outperforming bitcoin is interesting to me, as I’ve previously suggested attempting to value MSTR stock as priced in bitcoin rather than dollars. This then begs the question of whether an investment of bitcoin into MSTR shares will positively perform in bitcoin terms over time.
This valuation is very difficult by its nature, but can broadly be done by adding the bitcoin they currently hold on their balance sheet with an estimate of all the bitcoin they may ever acquire in the future, plus an allowance for other factors such as debt.
The landscape has shifted over this period, with Michael Saylor admitting that their strategy has evolved over time. The vital point that I missed when considering how MSTR might acquire more bitcoin in the future was their ability to issue considerable amounts of new equity into the market and achieve two things in doing so:
i) increasing bitcoin held per share of existing shareholders
ii) strengthen their balance sheet to take on more debt (since further debt issued would be a smaller proportion of their overall balance sheet).
“But where does the (btc) yield come from?”
This is not yield in the conventional sense, but nor is it Terra Luna. Firstly, this could come from profits from the business, which are relatively small. More relevantly, let’s consider how both the capital raises from debt and equity have served to increase the bitcoin held per share.
1. Equity “at the money” offerings
Much has been made of MSTR’s market cap (i.e. the overall value of the shares) trading above “Net Asset Value” (NAV) – which is essentially the value of their current bitcoin holdings plus the value of the conventional business, less debt. A multiple approach is used to describe how far above or below NAV this might be.
At the time of writing, the MSTR market cap stands at around $50bn and the value of their bitcoin holdings at $18bn. Given the conventional MSTR business is relatively small, it’s easy to see how this is approaching a multiple of 3x NAV.
If the share price is $240 and the net asset value is only $80 per share, MSTR can then issue more equity at $240, buy more bitcoin with this, and by doing so increase the bitcoin per share of existing shareholders. What’s more, they can keep doing this as long as the share price remains high. As shown above, MSTR has coined the term “BTC yield” to measure how well they are performing at increasing bitcoin held per share.
2. Convertible Debt
This also generally serves to increase bitcoin held per share. To consider how, let’s consider one of the previous convertible debt offerings – those due in 2028 – works in practice
Amount borrowed – $1,010m
Annual interest rate payable – 0.625%
Conversion price – $183.2
As can see MSTR pays a very low interest rate, as most of the value of the bond is in the potential convertibility to MSTR equity at a price of $183.2. Ultimately there is a binary situation here – either the share price is above that level and they end up issuing more equity at that price, or it’s below, and they end up having simply borrowed money at a very low interest rate.
The crucial point is that the convertible bond conversion price is typically set at a premium of at least 30% to the current market share price, whilst MSTR are buying bitcoin at the outset with the bond proceeds.
Hence if all of this debt converts to equity (and all debt looks like it will at present – see slide below), they are typically managing to increase the BTC held per share for existing shareholders.
This is because in this example when the bonds are converted to shares at $183.2, this is done at a premium to the prior share price (let’s say for illustration it was $140) at which MSTR initially issued the debt and converted the borrowing proceeds to bitcoin.
[p16 of Q3 2024 Earnings Presentation]
It is these combined activities that have led to an impressive bitcoin yield of 17.8% for the year to date 2024, and leads to questions for how long this financial alchemy can continue. Some bitcoiners, such as the Quant Bros duo and True North* group (see both here) have spoken of a flywheel effect – the more Bitcoin MSTR can acquire and the higher the bitcoin per share metric goes, the higher the share price, which in turn increases their ability to issue yet more equity and debt to buy more bitcoin and further increase bitcoin per share.
*Side note – Michael Saylor used the phrase “True North” on the Earnings Call; likely not accidental.
One answer to how long this can continue is – as long as the equity and debt markets still show an appetite for snapping up the new debt and equity issuance, even if the share price is high. Michael Saylor characterises it as the beginning of the adoption of Bitcoin as digital capital for these markets, and MSTR constitutes the easiest exposure. They have established a monopoly of sorts – whilst it would feasibly be possible for a large company to catch them in Bitcoin held, it would still have a smaller proportion of its business exposed to Bitcoin than MSTR.
[p21 of Q3 2024 Earnings Presentation]
Volatility is vitality
Michael Saylor is very clear in this earnings call and other interviews that MicroStrategy’s share volatility is a feature and not a bug. It is more volatile than any other S&P stock. As can be seen below, the recent daily trading volume only trails to the very biggest companies in the S&P 500.
Saylor embraces this volatility. It is what gives the optionality component of their convertible debt its value, and allows the interest rate payable to be lower. In addition, when the share price is high MSTR can issue more equity and increase bitcoin per share.
The Earnings presentation makes reference to several different forms of Bitcoin exposure that MSTR can offer to the market now and in the future.
[p27 of Q3 2024 Earnings Presentation]
The MSTR “True North” Principles
The Q3 Earnings call saw the following principles outlined for the first time. The message is clear to the market – do not conflate the dollar volatility of MSTR’s share price with the nature of their Bitcoin principles, which (perhaps analogous to the Bitcoin protocol itself) are intended to be rock solid and consistent. In addition, Saylor cleared up one source of speculation – MSTR will not be seeking to purchase other companies to add to its potential for generating free cash flows to invest into Bitcoin.
[p34 of Q3 2024 Earnings Presentation]
Can’t stop, won’t stop
The Earnings call contained an ambitious plan to raise $42bn more capital over the next 3 calendar years. This would be $21bn worth of equity, by selling new shares into the market (known as an “at the money” equity option), and $21bn worth of fixed income debt. This was split as $10bn in 2025, $14bn in 2026 and $18bn in 2027.
There is no doubting the scale of this ambition – to date MSTR have issued in total around $4.3bn in convertible debt and $4.3bn in terms of issued equity.
One key point is clear in line with the principles listed above. Whilst Saylor wants to raise Capital at opportune times to best benefit shareholders in the long term and to achieve what he terms “intelligent leverage”, he doesn’t try and time his bitcoin buys.
Moreover, he is likely also not bothered that selling so much further equity into the market may not always benefit the share price in the short term.
[p33 of Q3 2024 Earnings Presentation]
Turning up the volume, but is anyone listening?
With this announcement of $42bn to come over the next 3 years, there is no end in sight with respect to MSTR’s thirst for further Bitcoin purchases.
And yet, there was little in the media around the announcement, and despite the share price performance topping the entire S&P 500 over the past 4 years, MicroStrategy sits nowhere on Google Trends in comparison to Bitcoin:
[Source: https://trends.google.co.uk/trends/explore?q=bitcoin,microstrategy&hl=en-GB]
For now, this is no Gamestop. There’s no huge amount of short interest, and the fabled retail crowds are nowhere to be seen. One thing’s for sure though. Buckle up.
Please get in touch with your thoughts and feedback.
-
 @ 0971cd37:53c969f4
2025-05-18 11:32:23
@ 0971cd37:53c969f4
2025-05-18 11:32:23ขุด Bitcoin หรือ Mining Bitcoin นั้นไม่ใช่เรื่องใหม่ แต่ในปัจจุบันการทำเหมืองขุดจากที่บ้าน(Home Miner)กลับมาได้รับความสนใจอีกครั้ง หลายๆคนกำลังหาเทคนิคให้คุ้มค่าและมีประสิทธิภาพสำหรับ Home Miner ที่ช่วยให้การขุดมีประสิทธิภาพมากขึ้นในบทความนี้
ก่อนเริ่มทำเหมืองขุดแบบ(Home Miner)ต้องนึกถึงสำรวจคิดทบทวนตัวเองว่าให้แน่ชัดเจน เป้าหมายเหมืองขุดBitcoin
- ทำเหมืองเพื่อสะสมออม Bitcoin โดยการใช้เครื่องขุด Bitcoin (ASIC)?
- ทำเพื่อเอา Bitcoin ขายเพื่อได้เงิน Fiat ใช้ และให้เป็นรายได้หลัก?
- เป็นผู้สร้างผลิตพลังงานใช้เองและเหลือพลังงานจากการผลิตเหมาะสมมั้ยที่จะทำเหมือง?
ทำเหมืองเพื่อสะสมออม Bitcoin โดยการใช้เครื่องขุด Bitcoin (ASIC)? ถ้าในกรณีทำเพื่อสะสมออม Bitcoin โดยการใช้เครื่องขุด ASIC (Application-Specific Integrated Circuit) นั้นถือเป็นวิธีที่เหมาะสมและมีประสิทธิภาพที่สุด เนื่องจาก ASIC ถูกออกแบบมาเฉพาะสำหรับการขุด Bitcoin โดยเฉพาะ ทำให้มีอัตราการขุด (Hashrate) ที่สูงและใช้พลังงานต่ำ
ข้อดี - Hashrate สูง สามารถขุด Bitcoin ได้รวดเร็วและมีโอกาสได้รับ Reward block Subsidy + fees มากขึ้น - ประหยัดพลังงาน ASIC ใช้พลังงานต่อ Hashrate ต่ำกว่า ในกรณีทำการ Tuning ASIC หรือ Low Power - ไม่จำเป็นต้องซื้อ Bitcoin ใน Exchange ไม่ต้อง KYC ไม่ต้องหาจังหวะการเข้าซื้อ Bitcoin ความผันผวนของราคาบน Exchange
ข้อเสีย
- ราคาสูง: ต้นทุนในการซื้อ ASIC ค่อนข้างสูง
ทำเหมืองเพื่อสร้างรายได้หลักจากการขาย Bitcoin? ถ้าในกรณีการทำเหมือง Bitcoin มองเป็นแหล่งรายได้หลักแต่ต้องบริหารมีการจัดการที่ดีด้วยเช่นกัน
ข้อดี - สร้างรายได้ประจำ หากสามารถคำนวณต้นทุนและรายได้ได้ดี จะสามารถขาย Bitcoin เป็นรายได้หลัก - มีสภาพคล่องสูง Bitcoin สามารถแลกเป็นเงินสด (Fiat) ได้อย่างรวดเร็วใน Exchange - ขยายระบบได้ง่าย สามารถเพิ่มเครื่องขุดเพื่อขยายกำลังการผลิต Hashrate เท่าที่จำเป็นความเหมาะสม สำหรับ Home Miner
ข้อเสีย
- ความผันผวนของราคา: ราคา Bitcoin มีการเปลี่ยนแปลงตลอดเวลา ทำให้ไม่สามารถคาดการณ์รายได้ได้แน่นอน
- การแข่งขันสูง จำนวนผู้ขุดมากขึ้นทำให้ Difficulty เพิ่มขึ้นเรื่อย ๆ
- ต้นทุนค่าไฟและค่าดูแล หากไม่จัดการพลังงานให้ดี ต้นทุนอาจสูงจนไม่คุ้มค่า
เป็นผู้สร้างผลิตพลังงานใช้เองและเหลือพลังงานจากการผลิตเหมาะสมมั้ยที่จะทำเหมือง? หากสามารถผลิตพลังงานไฟฟ้าใช้เองจากแหล่งพลังงานสะอาด เช่น โซล่าเซลล์ ความเหมาะสมการนำ พลังงานที่ผลิตได้มีเหลือใช้และไม่มีค่าเสียโอกาส การทำเหมืองขุด Bitcoin เล็กๆแบบ Home Miner ลดต้นทุนค่าไฟ,เพิ่มรายได้จากพลังงานส่วนเกิน, ลดระยะเวลาการคืนทุน ถือว่าคุ้มค่าที่จะทำ
จัดการพลังงานและค่าไฟฟ้า สำหรับ Home Miner หนึ่งในปัจจัยหลักของการขุดจากที่บ้านคือ ค่าไฟฟ้า ซึ่งสามารถลดลงได้ด้วยการ - มีโซล่าเซลล์ การใช้พลังงานแสงอาทิตย์เพื่อลดค่าไฟในช่วงกลางวัน - เลือกใช้มิเตอร์ TOU เลือกช่วงเวลาขุดการขุดในช่วง Off-Peak ที่ค่าไฟต่ำกว่าช่วง On-Peak - ทำการ Tuning ASIC เน้น Low Power
สรุปโดยรวม Home Miner เป็นวิธีหนึ่งการขุด Bitcoin ที่สามารถทำได้จากที่บ้าน หากมีการจัดการอุปกรณ์และพลังงานอย่างเหมาะสม รวมถึงการวางแผนการขุดในช่วงเวลาที่ค่าไฟฟ้าต่ำ และ การผลิตพลังงานเองจากโซล่าเซลล์ยังสามารถเพิ่มโอกาสในการลดต้นทุนและเพิ่มกำไรได้อีกด้วย
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-18 14:42:48
@ 5d4b6c8d:8a1c1ee3
2025-05-18 14:42:48What do we mean when we talk about "fitness"? The word implies a connection to a higher purpose: "Fitness for what?"
Biologically, "fitness" refers to the propensity of an organism to pass on it's genes. Biological fitness is clearly context dependent: i.e. an anaconda isn't so fit if it gets moved to the arctic. I think we can build on that, while making it more human.
I think of fitness as our capacity to thrive in our environment. That's going to be different for each of us, depending on our environment and our preferences. However, there are some useful implications of thinking of fitness this way: 1. Chores, errands, work, play, and family activities might be the best kind of exercise, since they are physical activities that are directly tied to your lifestyle. 2. Supplemental exercise should be geared towards your lifestyle and improving your ability to accomplish things you need to be able to do. 3. There's no such thing as a universal "best exercise" or "best diet", because we all have different fitness objectives. 4. "Fitness" is not static: We do different things and have different priorities at different points in our lives, so our fitness goals should change over time. Many of us will even have seasonal fitness changes, since we don't do the same things in winter as we do in summer.
How do you all think about "fitness"?
Is it a highfalutin ivory tower concept or is it just ABs?
https://stacker.news/items/982981
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 84b0c46a:417782f5
2025-05-18 12:38:22
@ 84b0c46a:417782f5
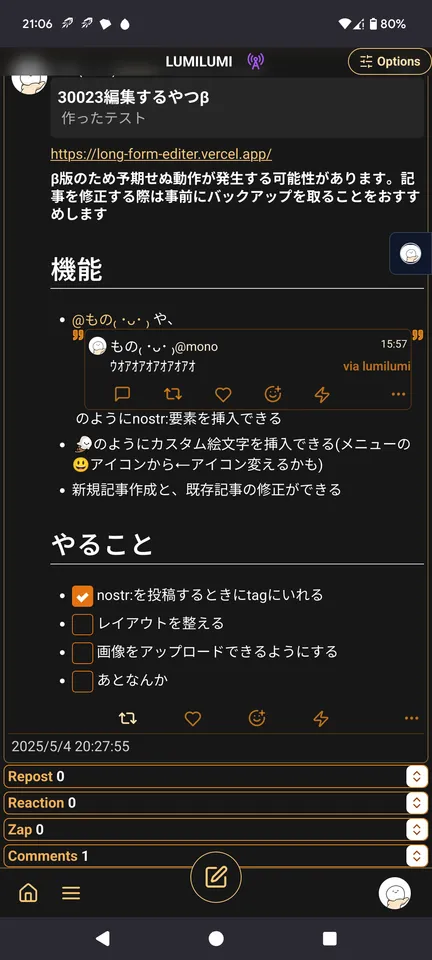
2025-05-18 12:38:22Simple Long Form Content Editor (NIP-23)
機能
-
nostr:npub1sjcvg64knxkrt6ev52rywzu9uzqakgy8ehhk8yezxmpewsthst6sw3jqcw や、 nostr:nevent1qvzqqqqqqypzq4jsz7zew5j7jr4pdfxh483nwq9vyw9ph6wm706sjwrzj2we58nqqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyxhwumn8ghj7mn0wvhxcmmvqqsgcn99jyn5tevxz5zxsrkd7h0sx8fwnqztula423xh83j9wau7cms3vg9c7 のようにnostr:要素を挿入できる (メニューのNアイコンから挿入またはnostr:note~~のように手動で入力)
-
:monoice:のようにカスタム絵文字を挿入できる(メニューの🙂アイコンから)
:monopaca_kao:
:kubipaca_karada:
- 新規記事作成と、既存記事の修正ができる
やることやったこと
-
[x] nostr:を投稿するときにtagにいれる
-
[x] 画像をアップロードできるようにする(NIP-96)
 できる
できる - [x] 投稿しましたログとかをトースト的なやつでだすようにする
- [ ] レイアウトを整える
- [ ] あとなんか
-
-
 @ 4c191b5d:c42abba6
2025-05-18 14:42:00
@ 4c191b5d:c42abba6
2025-05-18 14:42:00Eine kritische Auseinandersetzung mit Poppers Toleranzparadoxon
Vor kurzem wurde in einer Diskussion wieder argumentiert, man dürfte nicht tolerant sein mit Verweis auf Poppers Toleranzparadox.
Vielleicht habt ihr dieses Argument in Bezug auf unterschiedliche Themen (Corona, Krieg, Klima, Energie) auch schon gehört. Bei mir löst diese Forderung ein deutliches Störgefühl aus, da genau dieses Argument dafür genutzt wird, um die eigene Position zu verteidigen und andere auszugrenzen. Ich habe dies zum Anlass genommen, und mich intensiver mit der Frage beschäftigt, warum Popper irrte oder Menschen ihn falsch verstehen.
Denn ich begegne Immer wieder dem Argument, dass man nicht zu tolerant sein dürfe, um unsere Gesellschaft vor Intoleranz zu schützen. Dieses Argument stützt sich häufig auf Karl Poppers Toleranzparadoxon, das besagt, dass uneingeschränkte Toleranz gegenüber Intoleranz letztlich die Zerstörung einer toleranten Gesellschaft ermöglicht. Doch je mehr ich darüber nachdenke, desto mehr fallen mir problematische Aspekte dieses Konzepts auf.
Die menschliche Konfliktfähigkeit und Glasls Konfliktdynamik
Menschen sind von Natur aus emotionale Wesen, und unsere Fähigkeit, Konflikte konstruktiv zu lösen, ist oft begrenzt. Der Konfliktforscher Friedrich Glasl hat mit seinem Modell der neun Eskalationsstufen gezeigt, wie Konflikte schleichend von einer sachlichen Meinungsverschiedenheit zu einer destruktiven Auseinandersetzung eskalieren können.
In den frühen Stufen sind wir vielleicht noch in der Lage, rational zu diskutieren und Lösungen zu finden. Aber sobald Emotionen ins Spiel kommen, fällt es uns schwer, zwischen Beobachtung und Bewertung zu unterscheiden. Wir nehmen Kritik persönlich, fühlen uns angegriffen und reagieren defensiv. Diese Dynamik kann dazu führen, dass wir uns in unseren Positionen verhärten und der Konflikt weiter eskaliert.
Wenn wir nun Poppers Paradoxon anwenden und Intoleranz nicht tolerieren, riskieren wir, diesen Eskalationsprozess zu beschleunigen. Anstatt Brücken zu bauen, reissen wir sie ein. Wir schliessen Menschen aus dem Dialog aus und nehmen ihnen die Möglichkeit, ihre Sichtweisen zu überdenken.
Wer bestimmt, was intolerant ist? Wer hat das Recht zu entscheiden, was als intolerant gilt und was nicht?
Ein zentrales Problem ist die Frage der Definitionsmacht. Unsere Wahrnehmung ist subjektiv, geprägt von persönlichen Erfahrungen, kulturellem Hintergrund und gesellschaftlichen Normen. Wenn jeder für sich beansprucht, die richtige Definition von Toleranz und Intoleranz zu kennen, entsteht ein gefährliches Machtgefälle. Gruppen könnten ihre eigenen Ansichten als Massstab setzen und abweichende Meinungen als intolerant brandmarken. Dies öffnet Tür und Tor für Willkür und Unterdrückung von Minderheitenmeinungen.
Die Gefahr gegenseitiger Beschuldigungen
In meinen Begegnungen habe ich oft erlebt, wie schnell Diskussionen eskalieren können, wenn beide Seiten sich gegenseitig der Intoleranz beschuldigen. Es entsteht ein Teufelskreis: Jede Partei sieht sich im Recht und die andere im Unrecht. Laut Glasls Konfliktdynamik verschärft sich der Konflikt, je mehr die Kommunikation abbricht und Feindbilder aufgebaut werden.
Anstatt den Konflikt zu lösen, vertiefen sich die Gräben. Die Bereitschaft zum Zuhören schwindet, Vorurteile verfestigen sich, und es entsteht eine Spirale der Eskalation, die schwer zu durchbrechen ist.
Unrealistische Annahmen über menschliches Verhalten
Poppers Paradoxon setzt voraus, dass Menschen in der Lage sind, ihre Emotionen zu kontrollieren und stets rational zu handeln. Doch sind wir ehrlich: Wie oft gelingt uns das wirklich? In hitzigen Debatten kochen die Emotionen hoch, und selbst die besten Argumente prallen ab.
Die Erwartung, dass wir immer sachlich bleiben können, ignoriert die Komplexität menschlicher Interaktionen. Wir sind keine Maschinen, sondern von Gefühlen geleitete Wesen. Diese Realität muss in Betracht gezogen werden, wenn wir über Toleranz und Intoleranz diskutieren.
Ein Plädoyer für Dialog und Verständnis
Anstatt Intoleranz mit Intoleranz zu begegnen, sollten wir uns bemühen, den Dialog zu suchen. Das bedeutet nicht, dass wir hasserfüllte oder menschenfeindliche Äusserungen akzeptieren müssen. Aber wir sollten versuchen, die Ursachen solcher Einstellungen zu verstehen und durch Aufklärung und Bildung entgegenzuwirken.
Durch offene Gespräche können Vorurteile abgebaut und Missverständnisse geklärt werden. Es geht darum, Brücken zu bauen, anstatt Mauern zu errichten. Nur so können wir langfristig eine wirklich tolerante Gesellschaft fördern.
Fazit
Poppers Toleranzparadoxon wirft wichtige Fragen auf, doch seine praktische Anwendung ist mit erheblichen Schwierigkeiten verbunden. Die menschliche Neigung zur Eskalation von Konflikten, wie von Glasl beschrieben, sowie die subjektive Wahrnehmung von Intoleranz erschweren eine klare Umsetzung.
Wir sollten uns darauf konzentrieren, die Konfliktfähigkeit der Menschen zu stärken und Räume für konstruktive Auseinandersetzungen zu schaffen. Toleranz bedeutet nicht, alles hinzunehmen, sondern offen für andere Sichtweisen zu sein und gemeinsam nach Lösungen zu suchen.
In einer Welt, in der mir immer wieder das Argument begegnet, man dürfe nicht zu tolerant sein, plädiere ich dafür, dass wir unsere Definition von Toleranz überdenken. Es geht nicht um Nachgiebigkeit gegenüber Intoleranz, sondern um den mutigen Schritt, aufeinander zuzugehen und den Dialog zu suchen. Nur so können wir verhindern, dass wir in die Fallen der Eskalation tappen und die Werte verlieren, die unsere Gesellschaft ausmachen.
-
 @ b99efe77:f3de3616
2025-05-18 10:09:42
@ b99efe77:f3de3616
2025-05-18 10:09:42🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ b99efe77:f3de3616
2025-05-18 10:07:16
@ b99efe77:f3de3616
2025-05-18 10:07:16🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ b99efe77:f3de3616
2025-05-18 10:03:06
@ b99efe77:f3de3616
2025-05-18 10:03:06🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ b99efe77:f3de3616
2025-05-18 09:31:00
@ b99efe77:f3de3616
2025-05-18 09:31:00My everyday activity
This template is just for demo needs.
Places & Transitions
- Places:
-
Bla bla bla: some text
-
Transitions:
- start: Initializes the system.
- logTask: bla bla bla.
petrinet ;startDay () -> working ;stopDay working -> () ;startPause working -> paused ;endPause paused -> working ;goSmoke working -> smoking ;endSmoke smoking -> working ;startEating working -> eating ;stopEating eating -> working ;startCall working -> onCall ;endCall onCall -> working ;startMeeting working -> inMeetinga ;endMeeting inMeeting -> working ;logTask working -> working -
 @ 57c631a3:07529a8e
2025-04-07 13:17:50
@ 57c631a3:07529a8e
2025-04-07 13:17:50What is Growth Engineering? Before we start: if you’ve already filled out the What is your tech stack? survey: thank you! If you’ve not done so, your help will be greatly appreciated. It takes 5-15 minutes to complete. Those filling out will receive results before anyone else, and additional analysis from myself and Elin. Fill out this survey here.**
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
Growth engineering was barely known a decade ago, but today, most scaleups and many publicly traded tech companies have dedicated growth teams staffed by growth engineers. However, some software engineers are still suspicious of this new area because of its reputation for hacky code with little to no code coverage.
For this reason and others, I thought it would be interesting to learn more from an expert who can tell us all about the practicalities of this controversial domain. So I turned to Alexey Komissarouk, who’s been in growth engineering since 2016, and was in charge of it at online education platform, MasterClass. These days, Alexey lives in Tokyo, Japan, where he advises on growth engineering and teaches the Growth Engineering course at Reforge.
In today’s deep dive, Alexey covers:
- What is Growth Engineering? In the simplest terms: writing code to help a company make more money. But there are details to consider: like the company size where it makes sense to have a dedicated team do this.
- What do Growth Engineers work on? Business-facing work, empowerment and platform work are the main areas.
- Why Growth Engineers move faster than Product Engineers. Product Engineers ship to build: Growth Engineers ship to learn. Growth Engineers do take shortcuts that would make no sense when building for longevity – doing this on purpose.
- Tech stack. Common programming languages, monitoring and oncall, feature flags and experimentation, product analytics, review apps, and more.
- What makes a good Growth Engineer? Curiosity, “build to learn” mindset and a “Jack of all trades” approach.
- Where do Growth Engineers fit in? Usually part of the engineering department, either operating as with an “owner” or a “hitchiker” model.
- Becoming a Growth Engineer. A great area if you want to eventually become a founder or product manager – but even if not, it can accelerate your career growth. Working in Growth forces you to learn more about the business.
With that, it’s over to Alexey:
I’ll never forget the first time I made my employer a million dollars.
I was running a push notification A/B test for meal delivery startup Sprig, trying to boost repeat orders.
A push notification similar to what we tested to boost repeat orders
Initial results were unpromising; the push notification was not receiving many opens. Still, I wanted to be thorough: before concluding the idea was a failure, I wrote a SQL query to compare order volume for subsequent weeks between customers in test vs control.
The SQL used to figure out the push notification’s efficiency
As it turned out, our test group “beat” the control group by around 10%:
‘review_5_push’ was the new type of push notification. Roughly the same amount of users clicked it, but they placed 10% more in orders
I plugged the numbers into a significance calculator, which showed it was statistically significant – or “stat-sig” – and therefore highly unlikely to be a coincidence. This meant we had a winner on our hands! But how meaningful was it, really, and what would adding the push notification mean for revenue, if rolled out to 100% of users?
It turned out this experiment created an additional $1.5 million dollars, annually, with just one push notification. Wow!
I was hooked. Since that day, I've shipped hundreds of experimental “winners” which generated hundreds of millions of incremental revenue for my employers. But you never forget the first one. Moments like this is what growth engineering is all about.
1. What is Growth Engineering?
Essentially, growth engineering is the writing of code to make a company money. Of course, all code produced by a business on some level serves this purpose, but while Product Engineers focus on creating a Product worth paying for, Growth Engineers instead focus on making that good product have a good business. To this end, they focus on optimizing and refining key parts of the customer journey, such as:
- Getting more people to consider the product
- Converting them into paying customers
- Keeping them as customers for longer, and spending more
What kinds of companies employ Growth Engineers? Places you’ve heard of, like Meta, LinkedIn, DoorDash, Coinbase, and Dropbox, are some of the ones I’ve had students from. There’s also OpenAI, Uber, Tiktok, Tinder, Airbnb, Pinterest… the list of high-profile companies goes on. Most newer public consumer companies you’ve heard have a growth engineering org, too.
Typically, growth engineering orgs are started by companies at Series B stage and beyond, so long as they are selling to either consumers or businesses via SaaS. These are often places trying to grow extremely fast, and have enough software engineers that some can focus purely on growth. Before the Series B stage, a team is unlikely to be ready for growth for various reasons; likely that it hasn’t found product-market fit, or has no available headcount, or lacks the visitor traffic required to run A/B tests.
Cost is a consideration. A fully-loaded growth team consisting of a handful of engineers, a PM, and a designer costs approximately 1 million dollars annually. To justify this, a rule of thumb is to have at least $5 million dollars in recurring revenue – a milestone often achieved at around the Series B stage.
Despite the presence of growth engineering at many public consumer tech companies, the field itself is still quite new, as a discipline and as a proper title.
Brief history of growth engineering
When I joined Opendoor in 2016, there was a head of growth but no dedicated growth engineers, but there were by the time I left in 2020. At MasterClass soon after, there was a growth org and a dozen dedicated growth engineers. So when did growth engineering originate?
The story is that its origins lie at Facebook in 2007. The team was created by then-VP of platform and monetization Chamath Palihapitiya. Reforce founder and CEO Brian Balfour shares:
“Growth (the kind found on an org chart) began at Facebook under the direction of Chamath Palihapitiya. In 2007, he joined the early team in a nebulous role that fell somewhere between Product, Marketing, and Operations. According to his retelling of the story on Recode Decode, after struggling to accomplish anything meaningful in his first year on the job, he was on the verge of being fired.Sheryl Sandberg joined soon after him, and in a hail mary move he pitched her the game-changing idea that led to the creation of the first-ever growth team. This idea not only saved his job, but earned him the lion’s share of the credit for Facebook’s unprecedented growth.At the time, Sheryl and Mark asked him, “What do you call this thing where you help change the product, do some SEO and SEM, and algorithmically do this or that?”His response: “I don’t know, I just call that, like, Growth, you know, we’re going to try to grow. I’ll be the head of growing stuff."And just like that, Growth became a thing.”
Rather than focus on a particular product or feature, the growth team at Facebook focused on moving the needle, and figuring out which features to work on. These days, Meta employs hundreds if not thousands of growth engineers.
2. What do Growth Engineers work on?
Before we jump into concrete examples, let’s identify three primary focus areas that a growth engineer’s work usually involves.
- Business-facing work – improving the business directly
- Empowerment work – enabling other teams to improve the business
- Platform work – improving the velocity of the above activities
Let’s go through all three:
Business-facing work
This is the bread and butter of growth engineering, and follows a common pattern:
- Implement an idea. Try something big or small to try and move a key business metric, which differs by team but is typically related to conversion rate or retention.
- Quantify impact. Usually via A/B testing.
- Analyze impact. Await results, analyze impact, ship or roll back – then go back to the first step.
Experiments can lead to sweeping or barely noticeable changes. A famous “I can’t believe they needed to test this” was when Google figured out which shade of blue generates the most clicks. At MasterClass, we tested things across the spectrum:
- Small: should we show the price right on the homepage, was that a winner? Yes, but we framed it in monthly terms of $15/month, not $180/year.
- Medium: when browsing a course page, should we include related courses, or more details about the course itself? Was it a winner? After lengthy experimentation, it was hard to tell: both are valuable and we needed to strike the right balance.
- Large: when a potential customer is interested, do we take them straight to checkout, or encourage them to learn more? Counterintuitively, adding steps boosted conversion!
Empowerment
One of the best ways an engineer can move a target metric is by removing themselves as a bottleneck, so colleagues from marketing can iterate and optimize freely. To this end, growth engineers can either build internal tools or integrate self-serve MarTech (Marketing Technology) vendors.
With the right tool, there’s a lot that marketers can do without engineering’s involvement:
- Build and iterate on landing pages (Unbounce, Instapage, etc)
- Draft and send email, SMS and Push Notifications (Iterable, Braze, Customer.io, etc)
- Connect new advertising partners (Google Tag Manager, Segment, etc)
We go more into detail about benefits and applications in the MarTech section of Tech Stack, below.
Platform work
As a business scales, dedicated platform teams help improve stability and velocity for the teams they support. Within growth, this often includes initiatives like:
- Experiment Platform. Many parts of running an experiment can be standardized, from filtering the audience, to bucketing users properly, to observing statistical methodology. Historically, companies built reusable Experiment Platforms in-house, but more recently, vendors such as Eppo and Statsig have grown in popularity with fancy statistical methodologies like “Controlled Using Pre-Experiment Data” (CUPED) that give more signal with less data.
- Reusable components. Companies with standard front-end components for things like headlines, buttons, and images, dramatically reduce the time required to spin up a new page. No more "did you want 5 or 6 pixels here" with a designer; instead growth engineers rely on tools like Storybook to standardize and share reusable React components.
- Monitoring. Growth engineering benefits greatly from leveraging monitoring to compensate for reduced code coverage. High-quality business metric monitoring tools can detect bugs before they cause damage.
When I worked at MasterClass, having monitoring at the ad layer prevented at least one six-figure incident. One Friday, a marketer accidentally broadened the audience for a particular ad from US-only, to worldwide. In response, the Facebook Ad algorithm went on a spending spree, bringing in plenty of visitors from places like Brazil and India, whom we knew from past experience were unlikely to purchase the product. Fortunately, our monitoring noticed the low-performing campaign within minutes, and an alert was sent to the growth engineer on-call, who immediately reached out to the marketer and confirmed the change was unintentional, and then shut down the campaign.
Without this monitoring, a subtle targeting error like this could have gone unnoticed all weekend and would have eaten up $100,000+ of marketing budget. This episode shows that platform investment can benefit everyone; and since growth needs them most, it’s often the growth platform engineering team which implements them.
As the day-to-day work of a Growth Engineer shows, A/B tests are a critical tool to both measure success and learn. It’s a numbers game: the more A/B tests a team can run in a given quarter, the more of them will end up winners, making the team successful. It’s no wonder, then, that Growth Engineering will pull out all the stops to improve velocity.
3. Why Growth Engineers move faster than Product Engineers
On the surface, growth engineering teams look like product engineering ones; writing code, shipping pull requests, monitoring on-call, etc. So how do they move so much faster? The big reason lies in philosophy and focus, not technology. To quote Elena Verna, head of growth at Dropbox:
“Product Engineering teams ship to build; Growth Engineering teams ship to learn.”
Real-world case: price changes at Masterclass
A few years ago at MasterClass, the growth team wanted to see if changing our pricing model to multiple tiers would improve revenue.
Inspired in part by multiple pricing tiers for competitors such as Netflix (above), Disney Plus, and Hulu.
The “multiple pricing tier” proposal for MasterClass.
From a software engineering perspective, this was a highly complex project because:
- Backend engineering work: the backend did not yet support multiple pricing options, requiring a decent amount of engineering, and rigorous testing to make sure existing customers weren’t affected.
- Client app changes: on the device side, multiple platforms (iOS, iPad, Android, Roku, Apple TV, etc) would each need to be updated, including each relevant app store.
The software engineering team estimated that becoming a “multi-pricing-tier” company would take months across numerous engineering teams, and engineering leadership was unwilling to greenlight that significant investment.
We in growth engineering took this as a challenge. As usual, our goal was not just to add the new pricing model, but to learn how much money it might bring in. The approach we ended up proposing was a Fake Door test, which involves offering a not-yet-available option to customers to gauge interest level. This was risky, as taking a customer who’s ready to pay and telling them to join some kind of waiting list is a colossal waste, and risks making them feel like the target of a “bait and switch” trick.
We found a way. The key insight was that people are only offended about a “bait and switch”, if the “switch” is worse than the “bait.” Telling customers they would pay $100 and then switching to $150 would cause a riot, but starting at $150 and then saying “just kidding, it’s only $100” is a pleasant surprise.
The good kind of surprise.
So long as every test “pricing tier” is less appealing – higher prices, fewer features – than the current offering, we could “upgrade” customers after their initial selection. A customer choosing the cheapest tier gets extra features at no extra cost, while a customer choosing a more expensive tier is offered a discount.
We created three new tiers, at different prices. The new “premium” tier would describe the existing, original offering. Regardless of what potential customers selected, they got this “original offering,” during the experiment.
The best thing about this was that no backend changes were required. There were no real, new, back-end pricing plans; everybody ended up purchasing the same version of MasterClass for the same price, with the same features. The entirety of the engineering work was on building a new pricing page, and the “congratulations, you’ve been upgraded” popup. This took just a few days.
Within a couple of weeks, we had enough data to be confident the financial upside of moving to a multi-pricing-tier model would be significant. With this, we’re able to convince the rest of engineering’s leadership to invest in building the feature properly. In the end, launching multiple pricing tiers turned out to be one of the biggest revenue wins of the year.
Building a skyscraper vs building a tent
The MasterClass example demonstrates the spirit of growth engineering; focusing on building to learn, instead of building to last. Consider building skyscrapers versus tents.
Building a tent optimizes for speed of set-up and tear-down over longevity. You don’t think of a tent as one that is shoddy or low-quality compared to skyscrapers: it’s not even the same category of buildings! Growth engineers maximize use of lightweight materials. To stick with the tents vs skyscraper metaphor: we prioritize lightweight fabric materials over steel and concrete whenever possible. We only resort to traditional building materials when there’s no other choice, or when a direction is confirmed as correct. Quality is important – after all, a tent must keep out rain and mosquitoes. However, the speed-vs-durability tradeoff decision results in very different approaches and outcomes.
4. Tech stack
At first glance, growth and product engineers use the same tooling, and contribute to the same codebases. But growth engineering tends to be high-velocity, experiment-heavy, and with limited test coverage. This means that certain “nice to have” tools for product engineering are mission-critical for growth engineers.
Read more https://connect-test.layer3.press/articles/ea02c1a1-7cfa-42b4-8722-0165abcae8bb
-
 @ b99efe77:f3de3616
2025-05-18 09:29:33
@ b99efe77:f3de3616
2025-05-18 09:29:33🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
;start () -> greenLight1 redLight2
;toRed1 greenLight1 -> queue redLight1
;toGreen2 redLight2 queue -> greenLight2
;toGreen1 queue redLight1 -> greenLight1
;toRed2 greenLight2 -> redLight2 queue
;stop redLight1 queue redLight2 -> ()Places & Transitions
- Places:
- greenLight1: Indicates that the first traffic light is green.
- greenLight2: Indicates that the second traffic light is green.
- redLight1: Indicates that the first traffic light is red.
- redLight2: Indicates that the second traffic light is red.
-
queue: Acts as a synchronization mechanism ensuring controlled alternation between the two traffic lights.
-
Transitions:
- start: Initializes the system by placing tokens in greenLight1 and redLight2.
- toRed1: Moves a token from greenLight1 to redLight1, while placing a token in queue.
- toGreen2: Moves a token from redLight2 to greenLight2, requiring queue.
- toGreen1: Moves a token from queue and redLight1 to greenLight1.
- toRed2: Moves a token from greenLight2 to redLight2, placing a token back into queue.
- stop: Terminates the system by removing tokens from redLight1, queue, and redLight2, representing the system's end state.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> ()
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 84b0c46a:417782f5
2025-05-18 12:22:32
@ 84b0c46a:417782f5
2025-05-18 12:22:32- Lumilumi The Nostr Web Client.
Lightweight modes are available, such as not displaying icon images, not loading images automatically, etc.
-
MAKIMONO A lightweight Long Form Content Editor with editing functionality for your articles. It supports embedding Nostr IDs via NIP-19 and custom emoji integration.
-
Nostr Share Component Demo A simple web component for sharing content to Nostr. Create customizable share buttons that let users easily post to Nostr clients with pre-filled content. Perfect for blogs, websites, or any content you want shared on the Nostr network. Try the interactive demo to see how seamlessly it integrates with your website.
Only clients that support receiving shared text via URL parameters can be added to the client list. If your preferred client meets this requirement, feel free to submit a pull request.
-
Nostr Follow Organizer A practical tool for managing your Nostr follows(kind3) with ease.
-
NAKE NAKE is a powerful utility for Nostr developers and users that simplifies working with NIP-19 and NIP-49 formats. This versatile tool allows you to easily encode and decode Nostr identifiers and encrypted data according to these protocol specifications.
- chrome extension
- firefox add-on
-
Nostviewstr A versatile Nostr tool that specializes in creating and editing addressable or replaceable events on the Nostr network. This comprehensive editor allows you to manage various types of lists and structured content within the Nostr ecosystem.
-
Luminostr Luminostr is a recovery tool for Nostr that helps you retrieve and restore Addressable or Replaceable events (such as kind: 0, 3, 10002, 10000, etc.) from relays. It allows you to search for these events across multiple relays and optionally re-publish them to ensure their persistence.
-
Nostr Bookmark Recovery Tool Nostr Bookmark Recovery Tool is a utility for retrieving and re-publishing past bookmark events ( kind:10003,30001,30003 ) from public relays. Rather than automatically selecting the latest version, it allows users to pick any previous version and overwrite the current one with it. This is useful for restoring a preferred snapshot of your bookmark list.
-
Profile Editor Profile Editor is a simple tool for editing and publishing your Nostr profile (kind: 0 event). It allows you to update fields such as name, display name, picture, and about text, and then publish the updated profile to selected relays.
-
Nostr bookmark viewer Nostr Bookmark Viewer is a tool for viewing and editing Nostr bookmark events (kind: 10003, 30001, 30003). It allows users to load bookmark data from relays, browse saved posts, and optionally edit and publish their own bookmark lists.
-
Nostr Note Duplicater Nostr Note Duplicater is a tool that rebroadcasts an existing Nostr event from a relay to other selected relays.
-
 @ 078d6670:56049f0c
2025-05-18 07:53:13
@ 078d6670:56049f0c
2025-05-18 07:53:13Imagine having a personal assistant who could prompt you into riding a positive wave of creativity and warn you about a risky period of your life when you are cognitively distracted. An assistant that knows you better than you do, only because it has processing power and a database curated by you for you. A better you, created by you!
There is so much fear around AI. It will take jobs, it will realize how stupid humans are and take over the world. That’s if you believe AI can become conscious, not merely mimic human behaviour. But it can’t, it is just a super complex system programmed to interact with you better than before. Here is a explanation by @clif_high : Artificial Intelligence is retarded or AI & Bullshit
AI is still the best thing since the internet!
Imagine having a tool to gauge your personal life, impersonally. No judgement, only code. A tool that could correlate your behaviour with moon phases, seasons, diurnal rhythms, astrological cycles, birthdays (or any other metric); if any patterns exist, it can enlighten you. The same tool filters your inbox, takes action if necessary, alerts you, if necessary.
All the artwork you’ve created, you’ve appreciated, can be analyzed for future inspiration.
What you might need: personal diary (digital), personal journal (if there’s a difference), calendar, pictures, emails and a personal AI.
It could also curate a reading list for you, discovering literature it calculates will benefit you, including economic theory and psychology. We would need a feedback system so it didn’t leave the reservation.
Is there a danger it could mislead you? Maybe if you think AI is sentient, or it could miscalculate, so you would need to check its bias (and your own).
Think of your smartphone, but more capable and a lot more processing power. Not more intelligence, that’s reserved for the programmer. Unless you’re the programmer (but maybe it won’t be necessary to learn coding), or rather the prompt-engineer, then it is up to your intelligence as to how well you can set up your personal AI assistant. Maybe you need an assistant to help you set it up, like, that would be a great vocation: helping old people configure their AI.
The aim is create opportunities for more recreation time. Time spent being healthy. There could be a setting on your AI to prioritize saving time when connecting with other people’s AI, so both enjoy hyper-productivity and time for passion.
There are amazing groups of people concerned in making AI available to all free of bias, decentralized and open source:
- GPT4ALL
- @BrianRoemmele on X & readmultiplex.com
- Open Agents is working on making AI decentralized by securing it openly with the Bitcoin blockchain (@OpenAgentsInc on X).
- If you know of any others, please drop a reference in the comments.
It is essential for humanity that AI remains open source. If it is centralized and co-opted by private corporations in cahoots with government, we’re in big trouble (genocide, slavery, poverty, endless wars). Decentralized, transparent, open-source AI leads to better humans!
-
 @ 84b0c46a:417782f5
2025-05-18 12:18:41
@ 84b0c46a:417782f5
2025-05-18 12:18:41-
バーガーキング
-
バーミヤン 台湾カステラ
-
焼肉ライク
-
本屋でギータの練習本探してみるとか
-
シードしぐなーの材料 → 普通にHWW買ったほうがいい説
- https://github.com/SeedSigner/seedsigner/releases
- Raspberry Pi Zero v1.3 ← v1.3はヘッダピンを自分でつけないといけないからWHにしてWi-FiBluetoothを外すのがよい
- Raspberry Pi Zero W ← Wi-Fi外すのが少し面倒
- Raspberry Pi Zero WH ¥3500
- WaveShare 1.3inch LCD HAT【14972】1.3インチ 240×240 IPS LCDディスプレイHAT for RaspberryPi ¥1980
- Raspberry Pi Zero用スパイカメラ ¥3310
リボンの長さが色々ある seedsignerのケースによるけど多分短いやつでいける
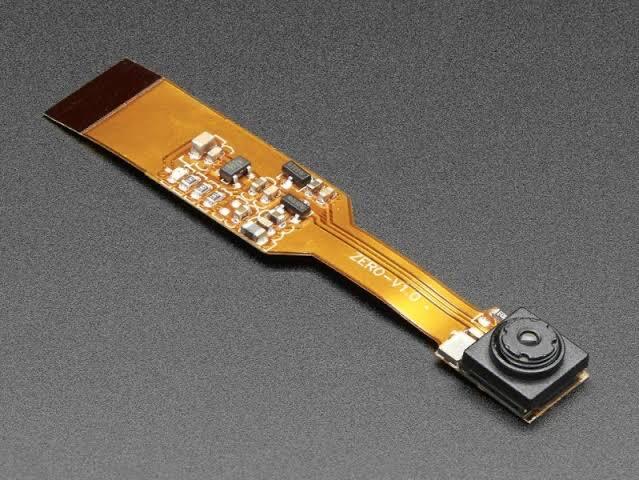 ↑こういうやつでいい
↑こういうやつでいい
 ↑ケースによってはこういうのがいい場合もある
↑ケースによってはこういうのがいい場合もある - https://github.com/SeedSigner/seedsigner/releases
-
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 84b0c46a:417782f5
2025-05-16 13:09:31
@ 84b0c46a:417782f5
2025-05-16 13:09:31₍ ・ᴗ・ ₎ ₍ ・ᴗ・ ₎₍ ・ᴗ・ ₎
-
 @ fbe736db:187bb0d5
2025-05-18 14:23:22
@ fbe736db:187bb0d5
2025-05-18 14:23:22This article was first published in July 2024 (and is best viewed) in the Bitcoin Collective here
Simon Sinek asks in his book “The Infinite Game” why more companies don’t operate with an infinite rather than a finite mindset. One main reason he misses, of course, is the money. The good news is there’s a new infinite game in town.
In “The Infinite Game”, Simon Sinek argues that great leaders set up their organisations to succeed beyond their own lifetimes. By recognising and positioning their business with an infinite rather than a finite mindset, they can engender greater trust throughout their employees and also build more resilience into their business. Their companies can also remain true to themselves and their mission, whatever that may be.
Sinek outlines that unfortunately we have entered an age of general subservience from leaders to their shareholders, and a slavery to the balance sheet and short term, “finite”, accounting and strategy. This generally leads to a decline of loyalty and engagement amongst customers and an increase in insecurity and anxiety amongst employees.
There’s plenty to agree with here in general terms. With that said, Sinek fails to identify one of the largest causes of the issues he identifies, which is the money. The book lays the blame on a watershed article from 1970 in which Milton Friedman laid out that “there is one and only one social responsibility of business, to use its resources and engage in activities designed to increase its profits so long as it stays within the rules of the game.” This is noted in the book as a turning point from the original ideas of Adam Smith, for whom the consumer was king, but I couldn’t help but wonder if anything else happened in the early 70s, such as Nixon cancelling the convertibility of dollars into gold in 1971. (see also – https://wtfhappenedin1971.com/).
Sinek bemoans the short term nature of companies since that point, but doesn’t consider how the nature of money has shaped this; surely a much more omnipresent and powerful factor than the writings of Milton Friedman. For the average bitcoiner this may be relatively self evident, but let’s consider the motives of the leadership under a system in which the underlying money cannot hold it’s value and in which credit is artificially priced. Incentives abound – one to laden the company with debt (which all else will likely diminish in real terms over time versus company assets and earnings), acquire other businesses and grow as big as possible in the process. Other options such as share buybacks also reflect short term incentives. Shareholders are going to place their own high short term demands on companies in a world where it is hard to outrun monetary debasement.
What of new businesses? When a new private entity is formed, the business plan is written, agreement on its viability is formed, strategy is set, tactics are agreed and then the first question posed by external stakeholders or posed to the majority shareholders is ‘what is your exit strategy’. Small successful businesses are expected to have a 3-5 year plan, private equity is usually a 3-5 year plan, and the successful larger companies with a longer trajectory also tend to swallow up the smaller successful companies (easier access to debt). With such incentives, it’s no wonder that we tend to see certain outcomes. There are obvious agency problems the larger a company gets, and they are more likely to fail to adhere to an infinite game principle. Smaller companies are forever at risk of getting swallowed up by larger ones.
So how does Bitcoin come into this? In my view, in two ways:
1. Bitcoin is an infinite game within itself
This is one of the subtle but crucial differences that splits Bitcoin sceptics and bitcoiners, and then dominates their onward arguments. If interpreted as a finite game, Bitcoin is for gambling, for speculation, it will have an end, and will be defined by winners and losers. Just the other day, this article framed it as such with the following line – “Whether Bitcoin is rising or falling, or who is buying or not buying it, nothing alters a basic fact: that Bitcoin is a classic zero-sum game. Large numbers of people can make vast paper fortunes by bidding up the price, but they cannot all realise those fortunes, because if everyone sells out the price collapses to zero. In that situation, those who were quick to sell would become rich at the expense of those who were slow to sell.”
Herein lies the problem for this criticism. As far as I can possibly ascertain right now, Bitcoin doesn’t end. Plenty might treat it as a finite game (and dismiss it as a ponzi, or try and trade it), but that treatment is a one way journey, and once you see Bitcoin as an infinite game there is little going back.
Going back to the book, let’s consider the “just cause” that Sinek says all businesses should have. According to Sinek, a just cause defines “the world we hope to live in and will commit to help build. It is the just cause that we are working to advance that gives our work and lives meaning. We know a cause is just when we commit to it with the confidence that others will carry on our legacy.” There are criteria listed too – a just cause must be “inclusive, service orientated, resilient, and idealistic.” Bitcoin surely fulfils these. On the ideology point, Michael Saylor articulated this well when dismissing altcoins in comparison to Bitcoin on the What Is Money podcast –
“If you really want a crypto to be successful over 100 years, the technology is only a part of it, right? It’s the ideology paired with the technology. And you’re gonna have to have an ideology that is so pure and so straightforward that people will fight to the death to defend the ideology. And that’s why I’m probably not gonna sacrifice my life for the 13th iteration on smart contracts. It’s not that important. On the other hand, if you tell me that we’re about to suck all of the economic energy out of the civilization and plunge ourselves into the Dark Ages, then I think I’ll fight for it. That’s worth fighting for.”
Michael Saylor – What is Money Show Episode 8
2. Bitcoin on balance sheets
Any business embracing Bitcoin on its balance sheet will automatically be closer to playing an infinite game itself, and let’s consider why. For starters, any shareholders will likely be holding equity with one opportunity cost being a holding of an equivalent amount of Bitcoin instead. This in itself will give them a low time preference mindset, which should transfer onto the company. Secondly, the act of having Bitcoin on the balance sheet provides a very simple yet iron clad discipline upon the company. One goal in broad terms is to grow that Bitcoin balance sheet over time, and they can only achieve that by being profitable. If they are not, they will find that Bitcoin balance dwindling over time instead. Though conventional businesses do broadly have the same need to be profitable, the Bitcoin example is quite different from a business with requirements to service debt, which may carry much shorter term deadlines for payment. In conclusion, companies looking to grow their Bitcoin holdings on a balance sheet are far more likely to buy into an infinite game mindset.
There are examples of infinite minded leaders out there, of course. Elon Musk is perhaps the most relevant in the present day, given Tesla and SpaceX have lofty long term ideals far removed from satisfying shareholders. Steve Jobs is another obvious one, and Sinek quotes an anecdote about sharing a cab with a senior Apple executive and telling him that the latest Microsoft Zune product (mp3 player at the time) was so much better than the Ipod touch. The executive smiled politely and was unfazed – tellingly, Apple weren’t worried about competitors in the short term due to their infinite mindset in making great & innovative products. Fast forward to today and there is evidence that Apple aren’t playing the infinite game that they used to. Take for example the recent news that Apple is plugging in Open AI into the iPhone. This doesn’t feel like the same ethos of a company who famously told us to “Think different” under Steve Jobs.
In conclusion, there’s plenty of decent ideas in the text and he articulates the issues well. However, due to failing to identify probably the main cause of the problem, Sinek doesn’t quite nail the call to arms for leaders to embrace an infinite game. Add in Bitcoin though, and the time preference of companies and their shareholders would vastly decrease and an infinite game mindset would come naturally.
One final thought – Sinek opens by looking back to the Vietnam war. Despite their vastly superior army and losing far fewer men, the US still lost the war. The reason being – it was an example of a finite mindset (thinking there would be a simple beginning and end) coming up against an infinite game and an enemy with an infinite mindset. The USA had comparatively infinite resources, infinite money, but a finite purpose & ideology when it came to the war. By contrast the Vietnamese, as one of their foreign ministry specialists was quoted as saying, were fighting for their independence and had already been doing so for thousands of years.
As far as Bitcoin is concerned, it might be said that companies who adopt a Bitcoin strategy are playing an infinite game with a non-debt based money of finite supply, and the competition are playing a finite game with an infinite supply of debt-based money.
This is a guest blog by Bitcoin Actuary / BitcoinActuary@BitcoinNostr.com. Thanks go to @btconlyscott for early comments/suggestions on this article.
This article is for information and education purposes only and is not intended as promotional material in any respect. All posts are the opinion of the author and should not be construed as investment advice and the opinions expressed do not necessarily reflect the views of The Bitcoin Collective Ltd.
-
 @ c230edd3:8ad4a712
2025-05-18 12:47:07
@ c230edd3:8ad4a712
2025-05-18 12:47:07Out of the night that covers me,
Black as the Pit from pole to pole,
I thank whatever gods may be
For my unconquerable soul.
In the fell clutch of circumstance
I have not winced nor cried aloud.
Under the bludgeonings of chance
My head is bloody, but unbowed.
Beyond this place of wrath and tears
Looms but the Horror of the shade,
And yet the menace of the years
Finds, and shall find, me unafraid.
It matters not how strait the gate,
How charged with punishments the scroll,
I am the master of my fate:
I am the captain of my soul.
-
 @ 84b0c46a:417782f5
2025-05-08 06:28:42
@ 84b0c46a:417782f5
2025-05-08 06:28:42至高の油淋鶏の動画 https://youtu.be/Ur2tYVZppBU のレシピ書き起こし
材料(2人分)
- 鶏モモ肉…300g
- A[しょうゆ…小さじ1 塩…小さじ1/3 酒…大さじ1と1/2 おろしショウガ…5g 片栗粉…大さじ1]
- 長ネギ(みじん切り)…1/2本(50g)
- ショウガ(みじん切り)…10g
- B[しょうゆ…大さじ2 砂糖…小さじ4 酢…大さじ1 ゴマ油…小さじ1 味の素…4ふり 赤唐辛子(小口切り)…1本分]
- 赤唐辛子、花椒(各好みで)…各適量
手順
- 肉を切る
皮を上にして適当に八等分くらい
- 肉を肉入ってたトレーかなんか適当な入れ物に入れてそこに 醤油こさじ1、塩こさじ1/3、酒おおさじ1と1/2 と ショウガ*5グラムすりおろして入れて軽く混ぜる
- そこに、片栗粉おおさじ1入れて混ぜる(漬ける段階にも片栗粉を入れることで厚衣になりやすい)
- 常温で15分くらい置く
- その間にたれを作る
-
長ネギ50gを細かいみじん切りにしてボウルに入れる(白いとこも青いとこも)
(端っこを残して縦に切り込みを入れて横に切るとよい) 2. ショウガ10gを細かいみじん切りにして同じボウルにいれる 3. 鷹の爪1本分入れる(任意) 4. 醤油おおさじ2、砂糖小さじ4、酢(穀物酢)おおさじ1を入れる 5. 味の素4振りいれてよく混ぜる 6. 小さなフライパン(油が少なくて済むので)に底に浸るくらいの油を入れ、中火で温める 7. 肉に片栗粉をたっぷりつけて揚げる 8. 揚がったらキッチンペーパーを敷いたなにかしらとかに上げる 9. もりつけてタレをかけて完成
-
-
 @ c1e9ab3a:9cb56b43
2025-05-18 04:14:48
@ c1e9ab3a:9cb56b43
2025-05-18 04:14:48Abstract
This document proposes a novel architecture that decouples the peer-to-peer (P2P) communication layer from the Bitcoin protocol and replaces or augments it with the Nostr protocol. The goal is to improve censorship resistance, performance, modularity, and maintainability by migrating transaction propagation and block distribution to the Nostr relay network.
Introduction
Bitcoin’s current architecture relies heavily on its P2P network to propagate transactions and blocks. While robust, it has limitations in terms of flexibility, scalability, and censorship resistance in certain environments. Nostr, a decentralized event-publishing protocol, offers a multi-star topology and a censorship-resistant infrastructure for message relay.
This proposal outlines how Bitcoin communication could be ported to Nostr while maintaining consensus and verification through standard Bitcoin clients.
Motivation
- Enhanced Censorship Resistance: Nostr’s architecture enables better relay redundancy and obfuscation of transaction origin.
- Simplified Lightweight Nodes: Removing the full P2P stack allows for lightweight nodes that only verify blockchain data and communicate over Nostr.
- Architectural Modularity: Clean separation between validation and communication enables easier auditing, upgrades, and parallel innovation.
- Faster Propagation: Nostr’s multi-star network may provide faster propagation of transactions and blocks compared to the mesh-like Bitcoin P2P network.
Architecture Overview
Components
-
Bitcoin Minimal Node (BMN):
- Verifies blockchain and block validity.
- Maintains UTXO set and handles mempool logic.
- Connects to Nostr relays instead of P2P Bitcoin peers.
-
Bridge Node:
- Bridges Bitcoin P2P traffic to and from Nostr relays.
- Posts new transactions and blocks to Nostr.
- Downloads mempool content and block headers from Nostr.
-
Nostr Relays:
- Accept Bitcoin-specific event kinds (transactions and blocks).
- Store mempool entries and block messages.
- Optionally broadcast fee estimation summaries and tipsets.
Event Format
Proposed reserved Nostr
kindnumbers for Bitcoin content (NIP/BIP TBD):| Nostr Kind | Purpose | |------------|------------------------| | 210000 | Bitcoin Transaction | | 210001 | Bitcoin Block Header | | 210002 | Bitcoin Block | | 210003 | Mempool Fee Estimates | | 210004 | Filter/UTXO summary |
Transaction Lifecycle
- Wallet creates a Bitcoin transaction.
- Wallet sends it to a set of configured Nostr relays.
- Relays accept and cache the transaction (based on fee policies).
- Mining nodes or bridge nodes fetch mempool contents from Nostr.
- Once mined, a block is submitted over Nostr.
- Nodes confirm inclusion and update their UTXO set.
Security Considerations
- Sybil Resistance: Consensus remains based on proof-of-work. The communication path (Nostr) is not involved in consensus.
- Relay Discoverability: Optionally bootstrap via DNS, Bitcoin P2P, or signed relay lists.
- Spam Protection: Relay-side policy, rate limiting, proof-of-work challenges, or Lightning payments.
- Block Authenticity: Nodes must verify all received blocks and reject invalid chains.
Compatibility and Migration
- Fully compatible with current Bitcoin consensus rules.
- Bridge nodes preserve interoperability with legacy full nodes.
- Nodes can run in hybrid mode, fetching from both P2P and Nostr.
Future Work
- Integration with watch-only wallets and SPV clients using verified headers via Nostr.
- Use of Nostr’s social graph for partial trust assumptions and relay reputation.
- Dynamic relay discovery using Nostr itself (relay list events).
Conclusion
This proposal lays out a new architecture for Bitcoin communication using Nostr to replace or augment the P2P network. This improves decentralization, censorship resistance, modularity, and speed, while preserving consensus integrity. It encourages innovation by enabling smaller, purpose-built Bitcoin nodes and offloading networking complexity.
This document may become both a Bitcoin Improvement Proposal (BIP-XXX) and a Nostr Improvement Proposal (NIP-XXX). Event kind range reserved: 210000–219999.
-
 @ b99efe77:f3de3616
2025-05-18 02:45:24
@ b99efe77:f3de3616
2025-05-18 02:45:24🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 78b3c1ed:5033eea9
2025-05-07 08:23:24
@ 78b3c1ed:5033eea9
2025-05-07 08:23:24各ノードにポリシーがある理由 → ノードの資源(CPU、帯域、メモリ)を守り、無駄な処理を避けるため
なぜポリシーがコンセンサスルールより厳しいか 1.資源の節約 コンセンサスルールは「最終的に有効かどうか」の基準だが、全トランザクションをいちいち検証して中継すると資源が枯渇する。 ポリシーで「最初から弾く」仕組みが必要。
-
ネットワーク健全性の維持 手数料が低い、複雑すぎる、標準でないスクリプトのトランザクションが大量に流れると、全体のネットワークが重くなる。 これを防ぐためにノードは独自のポリシーで中継制限。
-
開発の柔軟性 ポリシーはソフトウェアアップデートで柔軟に変えられるが、コンセンサスルールは変えるとハードフォークの危険がある。 ポリシーを厳しくすることで、安全に新しい制限を試すことができる。
標準ポリシーの意味は何か? ノードオペレーターは自分でbitcoindの設定やコードを書き換えて独自のポリシーを使える。 理論上ポリシーは「任意」で、標準ポリシー(Bitcoin Coreが提供するポリシー)は単なるデフォルト値。 ただし、標準ポリシーには以下の大事な意味がある。
-
ネットワークの互換性を保つ基準 みんなが全く自由なポリシーを使うとトランザクションの伝播効率が落ちる。 標準ポリシーは「大多数のノードに中継される最小基準」を提供し、それを守ればネットワークに流せるという共通の期待値になる。
-
開発・サービスの指針 ウォレット開発者やサービス提供者(取引所・支払いサービスなど)は、「標準ポリシーに準拠したトランザクションを作れば十分」という前提で開発できる。 もし標準がなければ全ノードの個別ポリシーを調査しないと流れるトランザクションを作れなくなる。
-
コミュニティの合意形成の場 標準ポリシーはBitcoin Coreの開発・議論で決まる。ここで新しい制限や緩和を入れれば、まずポリシーレベルで試せる。 問題がなければ、将来のコンセンサスルールに昇格させる議論の土台になる。
つまりデフォルトだけど重要。 確かに標準ポリシーは技術的には「デフォルト値」にすぎないが、実際にはネットワークの安定・互換性・開発指針の柱として重要な役割を果たす。
ビットコインノードにおける「無駄な処理」というのは、主に次のようなものを指す。 1. 承認される見込みのないトランザクションの検証 例: 手数料が極端に低く、マイナーが絶対にブロックに入れないようなトランザクション → これをいちいち署名検証したり、メモリプールに載せるのはCPU・RAMの無駄。
-
明らかに標準外のスクリプトや形式の検証 例: 極端に複雑・非標準なスクリプト(non-standard script) → コンセンサス的には有効だが、ネットワークの他ノードが中継しないため、無駄な伝播になる。
-
スパム的な大量トランザクションの処理 例: 攻撃者が極小手数料のトランザクションを大量に送り、メモリプールを膨張させる場合 → メモリやディスクI/O、帯域の消費が無駄になる。
-
明らかに無効なブロックの詳細検証 例: サイズが大きすぎるブロック、難易度条件を満たさないブロック → 早期に弾かないと、全トランザクション検証や署名検証で計算資源を浪費する。
これらの無駄な処理は、ノードの CPU時間・メモリ・ディスクI/O・帯域 を消耗させ、最悪の場合は DoS攻撃(サービス妨害攻撃) に悪用される。 そこでポリシーによって、最初の受信段階、または中継段階でそもそも検証・保存・転送しないように制限する。 まとめると、「無駄な処理」とはネットワークの大勢に受け入れられず、ブロックに取り込まれないトランザクションやブロックにノード資源を使うこと。
無駄な処理かどうかは、単に「ポリシーで禁止されているか」で決まるわけではない。
本質的には次の2つで判断される 1. ノードの資源(CPU、メモリ、帯域、ディスク)を過剰に使うか 2. 他のノード・ネットワーク・マイナーに受け入れられる見込みがあるか
将来のBitcoin CoreのバージョンでOP_RETURNの出力数制限やデータサイズ制限が撤廃されたとする。 この場合標準ポリシー的には通るので、中継・保存されやすくなる。 しかし、他のノードやマイナーが追随しなければ意味がない。大量に流せばやはりDoS・スパム扱いされ、無駄な資源消費になる。
最終的には、ネットワーク全体の運用実態。 標準ポリシーの撤廃だけでは、「無駄な処理ではない」とは断定できない。 実質的な「無駄な処理」の判定は、技術的制約+経済的・運用的現実のセットで決まる。
-
-
 @ b99efe77:f3de3616
2025-05-18 02:43:14
@ b99efe77:f3de3616
2025-05-18 02:43:14🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 9ca447d2:fbf5a36d
2025-05-18 11:36:05
@ 9ca447d2:fbf5a36d
2025-05-18 11:36:05Steak ‘n Shake recently made headlines by officially accepting bitcoin payments via the Lightning Network across all its U.S. locations. The integration of Bitcoin payments at over 500 locations is a monumental moment for both the fast food industry and the broader retail sector.
This is not just something that Steak ‘n Shake is testing in a handful of locations, they are doing a full-scale rollout, fully embracing Bitcoin.
With more than 100 million customers a year, Steak ‘n Shake’s integration of Lightning—Bitcoin’s fast, low-fee payment layer—makes it easier than ever to use Bitcoin in day-to-day life. Buying a burger and a shake with sats? That’s now a real option.
The process is straightforward. Customers simply scan a Lightning QR code at the register, completing their payment in seconds, while Steak ‘n Shake receives instant USD conversion, ensuring price stability and ease of use.
So what does this mean for Bitcoin and E-commerce?
For starters, Steak ‘n Shake becomes the first of eventually many to fully embrace a digital world. As Bitcoin continues to grow, consumers will continue to realize the benefits of saving in a currency that is truly scarce and decentralized.
This is a huge step forward for Bitcoin as it shows it is not just for holding, it’s for spending, too. And by using the Lightning Network, Steak n’ Shake is helping prove that Bitcoin can scale for everyday transactions.
This now creates a seamless checkout experience, making bitcoin a viable alternative to credit cards and cash.
More importantly, it signals a significant shift in mainstream attitudes towards Bitcoin. As a well-known brand across America, this move serves as a powerful endorsement, likely to influence other chains and retailers to consider similar integrations.
Related: Spar Supermarket in Switzerland Now Accepts Bitcoin Via Lightning
What can this mean for your business?
Accepting bitcoin as payment can open the door to a new demographic of tech-savvy, financially engaged consumers who prefer digital assets.
As we know, companies that adopt Bitcoin receive a fascinating amount of love from the Bitcoin community and I would assume Steak n’ Shake will be receiving the same amount of attention.
From a business perspective, accepting bitcoin has become more than just a payment method—it’s a marketing tool. It sets your business apart and gets people talking. And in a crowded market, that kind of edge matters.
Steak ‘n Shake’s embrace of Bitcoin is likely to accelerate the adoption of digital assets in both physical retail and e-commerce.
As more businesses witness the operational and marketing benefits, industry experts anticipate a ripple effect that will increase interaction between consumers and digital currencies, further regulatory clarity, and bring continued innovation in payment technology.
Steak ‘n Shake’s nationwide Bitcoin payments rollout is more than a novelty. It’s a pivotal development for digital payments, setting a precedent for other retailers and signaling the growing integration of digital assets into everyday commerce.
-
 @ b99efe77:f3de3616
2025-05-18 02:42:46
@ b99efe77:f3de3616
2025-05-18 02:42:46🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ a19caaa8:88985eaf
2025-05-06 00:14:49
@ a19caaa8:88985eaf
2025-05-06 00:14:49これって更新したらタイムラインに流れちゃう?それはいやかも テスト
-
 @ b99efe77:f3de3616
2025-05-18 02:42:12
@ b99efe77:f3de3616
2025-05-18 02:42:12🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 84b0c46a:417782f5
2025-05-04 09:49:45
@ 84b0c46a:417782f5
2025-05-04 09:49:45- 1:nan:
- 2
- 2irorio絵文字
- 1nostr:npub1sjcvg64knxkrt6ev52rywzu9uzqakgy8ehhk8yezxmpewsthst6sw3jqcw
- 2
- 2
- 3
- 3
- 2
- 1
|1|2| |:--|:--| |test| :nan: |
 ---
---:nan: :nan:
- 1
- 2
- tet
- tes
- 3
- 1
-
2
t
te
test
-
19^th^
- H~2~O
本サイトはfirefoxのみサポートしています うにょ :wayo: This text will bounce wss://catstrr.swarmstr.com/
うにょうにょてすと
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ b99efe77:f3de3616
2025-05-18 02:41:20
@ b99efe77:f3de3616
2025-05-18 02:41:20🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 84b0c46a:417782f5
2025-05-04 09:36:08
@ 84b0c46a:417782f5
2025-05-04 09:36:08 -
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 7460b7fd:4fc4e74b
2025-05-18 11:02:09
@ 7460b7fd:4fc4e74b
2025-05-18 11:02:09比特币持有者在 iPhone 上的安全使用注意事项
引言:iPhone 与安卓的对比
当涉及移动设备安全,比特币持有者面临着在 iPhone 和安卓设备之间的选择。从安全硬件来看,安卓阵营中确有一些型号配备了类似于 Apple Secure Enclave 的硬件安全模块,例如 Google Pixel 手机内置的 Titan M/M2 安全芯片,用于保障启动流程和存储敏感数据us.norton.com;三星的旗舰机型则集成了 Samsung Knox 多层安全平台,经过多国政府机构认证,可在硬件层面保护设备及其中数据us.norton.com。这些安全措施大大提升了设备抵御恶意攻击和数据泄露的能力。然而,需要注意的是:具备此类高级安全特性的安卓机型在市场上相对少见,并非安卓阵营的普遍标准us.norton.com。安卓生态高度碎片化,不同厂商的安全实践差异悬殊;除了少数注重安全的厂商(如 Google、Samsung)外,许多设备缺乏统一的安全保障水平us.norton.com。尤其在二手市场上,安卓设备型号繁杂且来源不一,一些旧款或改装机型可能缺少最新的安全芯片或更新,使安全性难以得到保证。
相比之下,Apple iPhone 全系列自带硬件级的安全隔区(Secure Enclave),统一的闭源系统和严格的应用审核使其安全措施在所有设备上保持一致us.norton.com。同时,iPhone 引入的 Face ID(三维结构光人脸识别)在生物识别安全性上具有独特优势。Apple官方数据显示,Face ID 被他人解锁的概率只有 百万分之一,远低于指纹识别的五万分之一。这源于Face ID利用红外点阵投射捕捉面部3D结构,难以被照片或面具所破解,大幅减少了伪造生物特征解锁的风险。此外,相较许多安卓手机仍依赖的二维人脸识别或电容/光学指纹,Face ID 在抗攻击能力上更胜一筹——例如普通指纹残留可能被提取复制,而二维人脸解锁曾被照片轻易骗过,但Face ID的深度感应技术有效避免了这些漏洞。
综上所述,在移动设备安全领域,iPhone 为比特币等高价值敏感资产的持有者提供了更为稳健和统一的安全基础。尽管某些高端安卓手机具有可圈可点的安全功能,但鉴于这类机型凤毛麟角、安卓设备更新和管控的不统一,以及生物识别方案的差异,我们强烈建议将 iPhone 作为比特币手持设备的唯一选择。从硬件加密到生物识别,iPhone 的封闭生态和领先技术能为数字资产提供更可靠的防护,而安卓设备在这一场景下则存在诸多先天不足。
小结: 安卓阵营虽有Pixel Titan芯片、Samsung Knox等亮点,但安全机型数量有限且良莠不齐;iPhone凭借统一的安全架构和先进的Face ID,在保护敏感数据方面更胜一筹。为确保比特币等资产安全,选择安全可靠的iPhone 是明智之举。
iPhone 安全配置指南
选择了 iPhone 作为比特币存取和通讯设备后,仍需进行细致的安全设置,以最大化利用其安全潜力。以下是针对比特币持有者的 iPhone 安全配置要点:
-
禁用 Face ID/Touch ID 生物解锁,改用强PIN码: 建议关闭面容ID解锁功能,改用6位以上的数字PIN码(或更复杂的字母数字密码)作为解锁方式。在紧急情况下,生物识别容易被他人强制利用(例如他人将手机对准机主面部强行解锁),而记忆型的PIN码只有持有人知晓,更难以被胁迫获取。此外,法律上某些地区对强制提供生物特征和提供密码有所区别,这也使得使用PIN码在极端情况下更有保障。
-
启用自动锁定(1分钟) 将设备设为闲置1分钟后自动锁定屏幕。从安全角度出发,锁定等待时间越短越好。1分钟的设置可确保即使暂时离开或疏忽,设备也会很快上锁,防范他人乘虚而入。养成随手锁屏的习惯固然重要,但有了短自动锁定时间作为双重保障,安全性更上一层楼。
-
开启输错10次自动抹除: 在“设置 > 面容ID/触控ID与密码”中启用“连续输错10次密码抹掉数据”功能。一旦有人反复尝试猜测密码,该功能会在第十次错误尝试后自动抹除手机数据。很多用户担心该设置存在风险,但事实上 误触发的可能性极低。sspai.comsspai.com实际测试表明,iPhone在多次输错密码时会触发累进的延迟惩罚机制:第五次错误需要等待1分钟,第六次错误等待5分钟,第7-8次各等待15分钟,第9次等待1小时sspai.comsspai.com。要连续进行十次独立的错误尝试至少需要约96分钟,在现实中“熊孩子”乱按连续清空数据几乎不可能发生sspai.com。相反,该功能对抗暴力破解极为有效——正如2015年圣贝纳迪诺恐怖袭击案中,嫌犯所用的iPhone就启用了十次错误清除,使FBI也无法轻易尝试破解en.wikipedia.org。总之,此项设置能将设备落入他人之手时的数据泄露风险降至最低。
-
利用应用级 Face ID 控制(iOS 18+):升级至iOS 18或更新版本,充分利用其新增的应用锁定功能。长按主屏某个应用图标,可以找到“需要Face ID”选项,将该应用加锁theverge.com。被加锁的应用每次打开都需要通过Face ID身份验证(即使手机已解锁)。建议对 聊天通讯、密码管理、交易所App 等敏感应用启用此功能。例如,将微信、Signal、邮件客户端等设置为打开需Face ID验证,以防范他人在您手机解锁的短暂间隙内获取其中内容。应用级Face ID锁定为设备提供了第二道防线:即使手机本身已解锁,敏感应用和数据仍受到保护。
-
建议购买第二台 iPhone 或 iPad 作为“备用解锁入口”: 利用 Apple 的“信任链”机制,为同一 Apple ID 配置多台受信任设备(如两台 iPhone 或 iPhone+iPad)。这样即使主设备丢失或被抹除,备用设备依然可以访问并恢复 iCloud 端到端加密数据。其安全本质类似于“1-of-N 多签”,即任一设备均可独立解锁所有云数据,但无需多设备联合协商,恢复更灵活。注意:这与比特币的m-of-n多签不同,Apple的信任链是单设备多入口,安全性和便利性权衡需根据个人需求评估。官方说明参见:Apple平台安全白皮书(Keychain与信任链)
-
建议购买 YubiKey 等硬件安全密钥作为 Apple ID 验证要素: 由于信任链机制下新设备加入时,身份验证成为潜在攻击点(如钓鱼、社工、短信劫持),推荐为 Apple ID 配置 YubiKey 或兼容 FIDO2/U2F 的硬件安全密钥。启用后,只有插入并触发硬件密钥的情况下,才能完成新设备授权、敏感操作或账户恢复,有效阻止网络钓鱼和大部分远程攻击。该方法可显著提升账户安全,降低因凭证泄漏或验证被劫持导致的信任链攻破风险。Apple 官方说明:为 Apple ID 添加安全密钥
通过上述配置,iPhone 将处于一个平衡了便利性和安全性的状态:日常解锁采用PIN码确保意外情况下设备不被强制解锁,短自动锁和十次清除严防暴力破解,而应用级加锁进一步保障重要数据不外泄。
小结: 按照以上指南对iPhone进行安全配置,可以大幅提升设备在实际使用中的抗攻击能力。生物识别解锁的取舍、自动锁定和清除机制、以及iOS 18引入的应用加锁功能相结合,全方位地巩固了手机作为比特币手持设备的安全基石。
关于自动抹除的常见质疑回应
启用“输错10次自动抹除”功能后,不少用户会提出疑虑,主要集中在两个方面:其一,担心儿童误操作或本人一时疏忽导致设备数据被抹掉;其二,担心万一手机数据被抹除,设备本身价值受损。针对这些质疑,我们进行如下回应:
-
“熊孩子乱按怎么办?” 前文已提及,iPhone设计了渐进延时机制,使得连续十次错误输入并非易事sspai.comsspai.com。孩子无意识地反复点击相同数字,系统只视为一次错误sspai.com;而多次不同错误则会触发越来越长的锁定时间,很难真的连续试满十次sspai.com。实践中,要触发十次错误清除需要近两个小时且每次输入都不同,这种情景极不现实sspai.com。因此,只要平时看护好设备,误抹除几乎无需担心。相反,如果没有该功能,一旦设备遗失或被不法分子获取,后果将不堪设想——对方可以在足够时间和专业工具协助下尝试无限次解锁,从而获取您手机中的一切秘密。
-
“数据没了岂不可惜?” 我们强调,比特币持有者手机中存储的敏感信息价值远超设备本身。手机里可能有助记词、私钥线索、交易记录截图,甚至包含您社交账户中关于资产的对话。在攻击者眼中,这些数据的价值胜过一部手机。与其担心设备被误清除,不如担心设备落入他人之手数据遭泄露的风险。况且,对于重要数据您应当早有备份(下文将讨论启用iCloud云备份的问题)。即使真发生误清除,有备份在手也能恢复;但若数据被不法分子窃取,一旦造成资产损失将无法挽回。因此,从风险权衡来看,“宁可误删,不可被盗”——自动抹除是最后一道保障,在极端情况下保护您的数字资产不被侵害。
总而言之,这一功能的利远大于弊。儿童误触可以通过良好监护和系统延时设计来防范,而一旦启用,您将获得巨大的安心:手机若遭试图破解,可以自毁以保全数据安全。这正是比特币持有者应有的安全理念:舍弃设备保安全,数据和资产永远优先于硬件。随着良好备份策略的配合(例如iCloud加密备份),启用自动抹除几乎没有后顾之忧。
小结: 针对自动抹除功能的疑虑更多是误解。iPhone的机制使得误触发几率极低,而其提供的数据安全保障却是无可替代的。比特币等敏感资产持有者应放下顾虑,优先保护数据安全——哪怕代价是设备被清除,也胜过数据落入他人之手。
iCloud 备份的争议与建议
在确保本地设备安全的同时,妥善备份数据同样关键。对于比特币持有者而言,启用 iCloud 云备份可以提供额外的一层安心:万一设备遗失、损坏或被抹除后,仍有机会恢复重要信息。然而,围绕iCloud备份的安全性一直存在争议,我们在此详细分析并给出建议:
首先强烈建议在启用iCloud备份的同时,务必开启「高级数据保护」(Advanced Data Protection, ADP)。默认情况下,iCloud云备份的数据加密密钥由Apple掌管,这意味着苹果公司在法律要求下能够解密并提供您的备份数据support.apple.comsupport.apple.com。而开启高级数据保护后,备份所涉及的大部分数据将采用端对端加密,只有您的受信任设备掌握解锁密钥support.apple.com。据苹果官方说明,在ADP模式下,即便苹果公司也无法读取您的备份内容support.apple.com。因此,高级数据保护能够将使用云备份可能带来的隐私泄露风险降至最低(前提是您妥善保管好自己的账户和恢复密钥)。
启用云备份常见的疑虑是:“会不会把我的钱包私钥也备份上去,万一云被攻破岂不危险?” 实际上,多数主流比特币/加密钱包软件不会将核心密钥(如助记词或扩展公钥xpub)存储在云备份中。很多钱包在设计时就要求用户自行备份助记词,而不会把这些高度敏感的数据写入应用沙盒,可被iCloud备份抓取。同样地,一些钱包应用甚至提醒用户关闭iCloud备份以防助记词泄露support.wallet.coinex.com。换言之,开启iCloud备份并不会将您的私钥上传(除非个别钱包特别设置了云同步,但大多数非托管钱包都没有这么做)。当然,为审慎起见,您可以查阅所用钱包的文档或设置,确认其是否有备份敏感信息到云的选项,并据此做出取舍。
与此同时,我们更加关心的是其他应用的数据完整备份。对于比特币持有者来说,聊天记录、笔记文档和工作应用的数据往往同样敏感且重要。例如,常用通讯软件(微信、Telegram、Signal 等)中的聊天可能涉及交易细节或人脉网络;办公应用如钉钉、飞书则包含财务往来或业务资料。这些应用的数据都会包含在iCloud整机备份中并被完整保存,一旦手机丢失或损坏,可以通过云备份原样恢复。support.apple.com值得一提的是,在高级数据保护开启且不泄漏密钥的前提下,这些备份数据即使存储在苹果服务器上也是安全的,第三方无法解读其中内容。
进一步的好处是:利用备份进行调查取证。假设最坏情况发生——您的手机被抹除或遗失,但是事先有一份最新的iCloud备份。在紧急需要时,您可以在一台新的iPhone上恢复这份备份。在恢复完成后,切断新设备的网络连接(拔掉SIM卡或不连Wi-Fi)。由于备份恢复会还原您的应用登录状态和本地数据,新设备在离线情况下将维持原手机当时的登录环境。您可以打开聊天应用、邮件、照片等查看内容,就像原手机一样。离线操作确保应用不会因为检测到新设备而要求重新登录,也避免了云端数据被远程清除的可能。这对于事后取证、提供线索给执法部门或自我调查都极为有利。比如,若涉及盗窃诈骗案件,这部离线恢复的手机里保留的聊天记录、交易凭证可以作为关键证据。而一旦联网,这些应用可能出于安全考虑登出账户或拉取最新状态,反而不利于保留原始证据。因此,有意识地保存一份完整云备份,并在需要时以离线方式恢复,是一种非常巧妙的应对策略。
小结: 尽管人们对云备份心存疑虑,但通过启用高级数据保护,iCloud备份既能提供数据恢复便利,又充分保障了隐私安全。大多数加密钱包不会上传私钥等核心数据,而聊天、办公等应用的数据则可完整份以备不时之需。在平衡安全与可用性的前提下,开启iCloud备份(搭配ADP加密)是明智之举——它让您在设备意外损坏或丢失时依然有据可查、有据可证。
高级数据保护与密码学机制分析
最后,我们从更宏观的视角,结合真实案例和技术原理,深入探讨苹果设备与云服务的安全性,以及高级数据保护(ADP)所依赖的密码学机制。这部分将涵盖苹果在多个国家遭遇的解锁争议、ADP 的运作及其与实体安全密钥的配合、以及关于苹果是否存在解密后门的分析。
苹果与执法部门的解锁事件
过去数年间,多起高调事件凸显了设备加密与执法取证之间的矛盾。美国国会山骚乱事件(2021年1月6日)中,执法部门缴获了大量嫌疑人的手机。据报道,不少嫌犯使用的是iPhone,调查人员能够从苹果获取其中的数据 但途径主要是通过 iCloud 云备份 而非直接破解设备thedailybeast.com。由于当时高级数据保护尚未推出或未启用,苹果依然持有那些嫌疑人iCloud账户的备份密钥,因此在收到合法的执法请求后,苹果向FBI提供了嫌疑人的iCloud备份内容,其中包括视频、照片和聊天记录等关键证据thedailybeast.com。这些数据帮助当局重构了案件过程,也反映出如果用户没有使用端到端加密备份,云端数据在法律压力下并非牢不可破。
相反,在更早的**圣贝纳迪诺恐怖袭击案(2015)**中,FBI面对一部启用了强加密的嫌犯iPhone却陷入僵局。那是一个运行iOS 9的 iPhone 5C,开启了PIN码锁和10次输错清除功能en.wikipedia.org。由于该设备上的本地数据经过设备加密且苹果并不持有密钥,FBI无法提取其中信息,遂求助苹果公司要求破解。但苹果以维护所有用户安全为由拒绝编写后门固件来绕过安全限制,引发了一场著名的法律拉锯en.wikipedia.orgen.wikipedia.org。最终执法部门辗转通过第三方工具解锁了手机,但苹果的立场十分明确:即便面对恐怖主义案件,也不会为单次事件在系统中留下后门。这一事件凸显出现代iPhone设备本地加密之强大——在没有用户密码的情况下,即使连厂商都无能为力,除非另辟蹊径寻求系统或硬件漏洞。
iCloud 在中国与英国的访问争议
在不同国家,苹果围绕用户数据加密与政府监管的博弈也在上演。中国方面,自2018年以来苹果将中国大陆 iCloud 服务交由“云上贵州”公司运营,数据存储和加密密钥均留在境内zh.amnesty.org。依据中国《网络安全法》,云服务运营者有义务为执法和国家安全机关提供“技术支持和协助”zh.amnesty.org。这意味着若中国警方出于刑侦需要向云上贵州调取某用户的 iCloud 数据,该公司必须配合提供,几乎没有拒绝的空间zh.amnesty.org。更重要的是,苹果把中国用户的 iCloud 加密密钥也存放在中国,一旦收到合法命令要求解密数据,苹果和云上贵州只能遵从zh.amnesty.org。换言之,在标准数据保护模式下,中国当局有途径通过法律手段获取本地存储的iCloud明文数据。这引发了人们对隐私的担忧:如果没有端到端加密,中国的用户数据可能在政府要求下被查看。然而如果用户开启高级数据保护,使得苹果也无法解读备份内容,那么即便在中国,此举从技术上为用户争取到了更高的私密性(前提是中国地区允许开启ADP——截至目前,苹果并未在中国禁用该功能,国区用户依然可以自行启用高级数据保护support.apple.comsupport.apple.com)。
再看英国的情况。英国政府近年以打击犯罪和恐怖主义为由,不断向科技公司施压要求提供加密数据的后门访问权。2023年底,英国援引《调查权力法》(IPA)秘密向苹果发出“技术能力通知”(TCN),要求苹果在全球范围内为英国安全部门提供对加密iCloud内容的解锁途径cnbeta.com.tw。这实际上等同于要求苹果破坏其端到端加密体系,留出一个只有政府能用的后门。苹果对此断然拒绝,并做出强硬回应:宁愿撤除在英服务,也不会妥协安全底线cnbeta.com.tw。结果是,苹果选择在英国境内停止提供高级数据保护功能给新用户。已有启用ADP的英国用户被通知需在宽限期内手动将其关闭,否则将无法继续使用iCloud备份cnbeta.com.tw。苹果在声明中表示对此深感失望,但为了遵守当地法律别无他法cnbeta.com.tw。下面这张截图显示了英国用户在系统中看到的提示信息,明确告知ADP服务不再可用

苹果针对英国地区做出的ADP功能调整通知。英国政府要求能够解密用户数据,迫使苹果撤回了对英国用户的新端到端加密备份支持cnbeta.com.twcnbeta.com.tw。苹果声明强调只有用户本人才能解读其加密数据,并重申不会在产品中留下执法后门cnbeta.com.tw。
这一英国内外的罕见举措表明,各国政府正日益重视加密带来的执法障碍,而苹果则在平衡用户隐私和法律要求之间走钢丝。尽管英国的情况迫使苹果让步(取消当地ADP),但苹果并未真的为政府打造解密后门,而是通过限制功能来表明态度——这与其长期立场一致:绝不在加密产品中留后门,即使承受业务上的损失cnbeta.com.tw。
高级数据保护与安全密钥
高级数据保护(ADP) 是苹果于 iOS 16.2 引入的一项可选功能,其核心是在用户选择开启后,将包括设备备份在内的大部分 iCloud 数据升级为端到端加密存储support.apple.comsupport.apple.com。开启ADP有两个前提:账户已启用双重认证,以及设置了账户恢复联系人或恢复密钥,以防用户遗失访问权限support.apple.comsupport.apple.com。在ADP模式下,Apple不再持有绝大部分云数据的解锁密钥,这些密钥只存在于用户的受信任设备中support.apple.com。这意味着,即便苹果公司收到政府索取数据的要求或其服务器遭黑客攻击,没有密钥的加密数据对任何第三方都是无意义的乱码。正如苹果声明所言:“只有拥有数据的用户才能解密,Apple 无法访问端对端加密的数据”cnbeta.com.tw。可以说,ADP将用户云数据的主导权完全交还给用户自己,从而彻底消除了苹果方面潜在的数据泄露点。
为了进一步增强账户安全,苹果在_iOS 16.3_开始支持绑定实体安全密钥(如 YubiKey)作为 Apple ID 的额外两步验证方式sspai.com。过去Apple ID登录主要依赖密码+发送到受信设备的验证码,但假如用户Apple ID密码泄露,攻击者可能利用社会工程获取验证码。而引入实体安全密钥后,用户可以要求任何新的登录尝试都必须提供物理密钥认证才能完成。这相当于给 Apple ID 上了一把“硬件锁”。对于比特币持有者而言,这一步非常值得配置:即使黑客骗取了您的苹果账号密码,没有您的YubiKey或同类FIDO2安全密钥,他仍无法登录您的iCloud或停用您的ADP。安全密钥本身具有防钓鱼特性,它不会把可被重用的机密泄露给假网站,再加上密钥私藏于硬件内部不可导出,使得账户保护达到新的高度sspai.comsspai.com。简而言之,**“ADP + 硬件安全密钥”**的组合为用户云数据打造了双重护城河:前者确保云上数据加密不被窥探,后者确保账户本身不被劫持利用。
需要注意的是,启用ADP后如果遗失所有设备且忘记密码,苹果无法帮您找回数据support.apple.com。这就像您把保险箱钥匙只握在自己手里而不交给任何人保管,其安全性空前提高,但也意味着责任完全在您。因此请务必牢记Apple ID密码,保管好恢复密钥或紧急联系人。一旦平衡好便利与安全,这套机制将为您的数字资产提供堪比硬件钱包的云端保障。
后门密钥与私钥不可拆分性
现代加密体系的设计使得用户私钥与设备环境密不可分。在苹果的生态中,每台设备都拥有由硬件生成的唯一加密根密钥。例如,安全隔区(Secure Enclave)内嵌入了设备唯一标识符UID作为根密钥,UID由安全硬件随机生成并烧录至芯片中help.apple.com。这个UID既不与任何其他设备标识相关,也无法被设备外的任何人(包括苹果官方)获取help.apple.com。同时,用户的解锁密码与该UID进行数学“交织”(entangle),共同派生出加密密钥help.apple.com。换言之,设备硬件密钥和用户密码共同决定了数据加密密钥,没有这两者就无法还原密钥。这体现了用户私钥对设备及用户身份的强绑定——苹果没有第三方密钥可以绕过这一绑定关系help.apple.comhelp.apple.com。
从密码学角度来看,如果苹果试图在上述体系中插入一个额外的“后门密钥”,将面临巨大的技术困难,并且这样的异常极易被察觉。设想苹果通过异或(XOR)或 Shamir 密钥共享等方式,将一个后门密钥与用户密钥组合:
- 实现层面的异常:用户设备在正常情况下应当能够独立完成解密/签名操作。如果加入隐藏密钥份额,意味着设备单凭用户自己的密钥无法完成某些解密,必须依赖苹果持有的那一份。这样的改动会造成额外的密钥协商步骤或异常的解密失败。例如,若苹果将后门密钥与用户密钥异或生成实际工作密钥,那么单用用户密钥将无法解密出正确结果,设备可能需要静默地向苹果服务器请求密钥片段或进行额外计算。这类非预期的通信或计算步骤很容易被安全研究者通过流量分析或逆向工程发现端倪。再比如采用 Shamir’s Secret Sharing 等门限方案,如果苹果持有一份密钥碎片,设备在解密时就需要满足门限条件,这通常意味着需要苹果的参与或预置公钥,从而在协议日志中留下异常痕迹。任何偏离常规协议的做法——无论是多传输一段数据,还是多保存一段密钥信息——都可能成为研究者捕捉的线索。历史经验表明,密码协议中的“奇怪之处”往往预示潜在漏洞或后门:例如 NSA 推出的 Dual_EC_DRBG 伪随机数生成器由于使用了异常常数,被专家迅速怀疑存在后门;著名密码学家施奈尔(Bruce Schneier)就曾直言 Dual_EC_DRBG 中的后门“相当明显”,呼吁业界停止使用en.wikipedia.org。由此可见,试图暗中插入额外密钥会在数学实现上留下破绽,而资深密码学者和安全社区有足够能力识别这些反常之处。
进一步,从门限签名理论对比苹果现有密钥管理,可以加深这一不可行性的理解。门限密码学允许将密钥拆分给多方持有,只有达到预定门槛的份额才能重构密钥或执行签名解密toc.csail.mit.edumedium.com。其优点在于提高了密钥托管的安全性,需要多方协作才能解锁秘密。然而,这种机制是公开设计的一部分,各参与方和流程都是明示的。例如在某些区块链多重签名方案中,多个私钥持有者共同生成交易签名,每个人都知晓门限机制的存在。相较之下,苹果在产品中的密钥管理要么是完全由用户端掌握密钥(如iPhone本地数据加密,密钥存在Secure Enclave中),要么是在用户许可下由苹果代管(如传统iCloud云备份未启用高级加密时,苹果保存备份密钥)。苹果并没有公开采用“两方门限”的模式来和用户分享密钥,否则等于声明“用户单方无法完全掌控自己的解密权”。如果苹果暗中采用门限签名让自己持有一份密钥碎片,本质上就是一种**变相密钥托管(Escrow)**行为。这样的做法会明显偏离苹果宣称的零后门立场,与其在隐私政策中反复强调的原则相违背。值得注意的是,苹果在其官方隐私声明中明确表示:“我们从未在任何产品或服务中创建过后门或万能解锁主密钥”apple.com。因此,从理论和实践双重层面来看,用户私钥与潜在后门密钥是难以在不被发现的情况下拆分存在的。任何试图将二者解耦的举措都会引起体系架构的异常,进而难逃专家法眼。
加密社区对后门的发现与审计
在当今的安全生态中,不存在“悄无声息的后门”。一旦厂商试图在加密方案中掺入后门密钥,全球的密码学社区和安全研究人员都有多种手段将其揪出。下面从几个方面概述社区常用的后门检测与审计方法:
-
开源协议分析:安全专家偏好开源的软件和协议,因为源码透明意味着任何可疑的算法修改、密钥处理流程都暴露在公众视野中。通过阅读和形式化分析公开的协议规范,研究者可以发现是否有多余的密钥交换步骤或异常的参数。例如,Signal通信协议的源代码和技术细节是完全公开的,全球专家曾多次审阅其实现,验证其端到端加密未存在后门linkedin.com。事实证明,公开透明带来的是更严苛的监督,任何隐秘加入的密钥参数都有可能被审计人员发现。正如业内人士所指出的,Signal 采用开放源码意味着安全专家可以独立审计其代码以核实安全性linkedin.com。类似地,许多现代加密库都会经过社区审视,以确保其中没有“暗门”。
-
逆向工程与二进制审计:对于闭源的软件(例如苹果自身的系统组件),安全研究者会运用逆向工程技术来分析应用的二进制代码和运行时行为。一旦苹果的加密实现存在未公开的密钥使用,比如在本地程序中引用了某个神秘常量或调用了隐藏的密钥解密函数,逆向工程往往能还原这些逻辑。专业团队通过调试、反编译、动态埋点等方式重现协议的握手过程,查看每一步骤所用的密钥材料。如果过程中出现与官方文档不符的环节(例如本应由用户设备生成的密钥却从外部获取),将立即引发怀疑。此外,安全社区定期举办的漏洞挖掘和破解挑战赛也扮演重要角色——顶尖黑客会竞相攻破苹果设备的加密层,并公开报告发现的问题。过去这些努力揭示了一些实现漏洞(如内存越界、0day攻击途径),但从未曝出“苹果预留万能密钥”之类的后门。一例典型事件是2017年有黑客成功解密了Secure Enclave固件以研究其中机理,结果证实即便取得固件代码,攻击者仍无法提取到任何用户密钥或后门凭证ciso.economictimes.indiatimes.com。这一结论进一步增强了业界对苹果加密实现中无后门的信心。
-
网络流量与协议行为分析:加密协议往往涉及设备与服务器的交互流程。研究人员会抓包和监控这些网络流量,分析协议握手时交换的消息格式和内容。如果苹果尝试在密钥协商时暗中插入自己的公钥或请求额外数据,流量分析将捕捉到异常的报文模式。例如,在正常的端到端加密通信中,设备之间交换彼此的公钥证书,不应有第三方公钥悄然出现。而所谓“幽灵用户”后门提案正是要求服务提供商在群聊中偷偷加入一个看不见的第三方公钥。这样的方案被广泛批评因为它破坏了用户验证通信对端身份的机制,需要服务器隐藏通知才能欺骗用户lawfaremedia.org。密码学家指出,这将削弱认证过程并带来新漏洞,因此难以在不被发现的情况下实施lawfaremedia.org。由此可见,通过流量异常识别潜在后门是切实可行的。当年的GCHQ“幽灵用户”建议一提出,就被包括苹果在内的业界联合抵制,47家机构和专家联名公开信指出该做法“对网络安全构成严重威胁”internetsociety.orgsilicon.co.uk,可见社区对这类后门手段有高度警惕性。
-
独立审计和信任链验证:许多安全敏感的加密功能会接受独立机构的审计,以建立公众信任。比如苹果的 iCloud 钥匙串(Keychain) 采用多层加密和信任链机制,其设计文档表明敏感信息的密钥始终需要Secure Enclave参与才能解锁techrepublic.com。有第三方评估指出,钥匙串中的私密数据即便保存在云端也是经过高强度加密的,任何人(包括苹果)都无法直接读取明文techrepublic.com。这一架构经过多轮外部安全会议研讨和学者研究,至今未出现被植入后门的迹象。同样,苹果设备中的 Secure Enclave 安全隔区 也多次成为学术研究和黑客大会的焦点。研究人员通过攻击Secure Enclave找出了少数漏洞(例如早期A7-A11芯片存在硬件级漏洞ciso.economictimes.indiatimes.comciso.economictimes.indiatimes.com),但这些漏洞只是实现瑕疵,并非有意留出的后门。实际上,正是这些公开的审计和破解挑战证明了Secure Enclave的设计初衷:即使攻击者获得硬件或固件访问权,仍无法提取出主密钥ciso.economictimes.indiatimes.com。学术界和白帽黑客社区通过反复的审查和渗透测试,为苹果的“零后门”承诺提供了有力的背书。换言之,加密社区的独立审计机制确保了任何后门都难以隐藏;只有经得起各方检验的系统,才能真正赢得用户信任。
综上所述,在强大的社区监督下,任何后门密钥的存在都会留下蛛丝马迹,并最终被曝光。无论是协议分析、逆向工程还是实网监测,多层次的手段使得厂商无法神不知鬼不觉地在成熟加密方案中藏入后门。这也是为什么苹果等公司反复强调没有后门:一旦撒谎,终将被揭穿,信用荡然无存。
iCloud 钥匙串信任链下的全局数据加密密钥(DEK)机制研究
苹果的高级数据保护(Advanced Data Protection)引入了端到端加密,将大部分 iCloud 数据的密钥仅存储在用户的受信设备上support.apple.com。在该机制下,每个用户的 iCloud 帐户针对各数据类别生成自己的“全局”数据加密密钥(Data Encryption Key, DEK),这些密钥受 iCloud 钥匙串的信任链机制保护。下面将详细探讨全局 DEK 的生成、分发与封装,多设备场景下的生命周期变化,以及苹果保障 DEK 安全和确保服务器从未获取明文 DEK 的技术手段。
全局 DEK 的生成、更新与轮换
初始生成:当用户首次在支持的设备上启用高级数据保护时(需运行 iOS 16.2、macOS 13.1 等新版系统,并开启双重认证),系统会在该设备上本地生成全局数据加密密钥。实际上,每个受端到端加密保护的 iCloud 服务(例如云备份、照片、笔记等)都有各自的 CloudKit 服务密钥对,其私钥用作该类别数据的主加密密钥support.apple.comsupport.apple.com。这些服务密钥使用安全随机算法在用户受信设备上创建,具有唯一性,并由设备的安全硬件保护。启用高级数据保护时,设备会将之前由苹果保存的云端密钥从苹果的硬件安全模块(HSM)中删除,并生成新的服务密钥,以改用仅存储在用户设备上的密钥来加密云端数据support.apple.comsupport.apple.com。这一过程确保全局 DEK(即各服务的新密钥)仅存在于用户受信设备上,苹果服务器端不再持有其副本。
是否变化及何时变化:在正常使用中,全局 DEK(各服务密钥)的私钥一经生成会保持稳定,用于持续加密解密用户数据,并不会频繁更换。唯有在特定事件下才会轮换或更新密钥,例如用户启用高级数据保护时系统触发的一次性密钥轮换,以及用户后来关闭高级数据保护或怀疑密钥泄露时的情况support.apple.com。苹果文档指出,当用户打开高级数据保护时,设备会启动异步密钥轮换操作,为此前存储于苹果服务器的每个服务创建新的服务密钥support.apple.com。新数据随后使用新密钥加密,旧密钥无法解密新数据support.apple.com。同样地,当用户关闭高级数据保护返回标准保护时,设备会将原本仅存于本地的新密钥上传回苹果HSM,并可恢复使用先前的旧密钥support.apple.com。因此,可以总结:初始启用高级保护时会生成并切换到新的全局 DEK,此后这些密钥保持不变;如用户关闭功能则恢复旧密钥;除非再次启用或发生安全事件,系统通常不会主动更换全局 DEK。
值得注意的是,在极端情况下如果用户怀疑密钥泄露或设备失窃,用户可以选择通过重置整个端到端加密环境(例如先关闭再重新开启高级数据保护)来触发新的 DEK 生成,从而保护云端数据安全。然而,此操作会要求所有设备重新加入信任链,并重新上传数据副本加密后存储。
多设备环境下 DEK 的分发与封装
信任链机制: 苹果使用 iCloud 钥匙串的信任链(又称同步圈,circle of trust)来在多设备间安全同步全局 DEK。启用了高级数据保护后,属于用户 Apple ID 的所有受信设备共同构成一个加密信任链,每台设备都有一对用于同步的非对称椭圆曲线密钥(如 P-384)support.apple.com。当第一台设备生成全局 DEK 后,它会将这些密钥加入自身的 iCloud 钥匙串保护域,并通过 CloudKit 安全地共享给用户的其他设备support.apple.com。具体而言,设备会维护一份受信设备的公钥列表,并使用自身的私钥对列表签名后存储于 iCloud;只有持有用户账户密码或设备私钥者才能读取或篡改这份列表support.apple.com。这一机制保证了只有经过用户授权加入信任链的设备才能获取 DEK,其余任何第三方(包括苹果服务器)都无法读取信任链中的密钥数据support.apple.com。
密钥传递与封装:在多设备场景下,每台设备都会持有全局 DEK(各服务私钥)的一个副本,但这些副本始终以安全加密形式封装后再传输和存储。例如,当用户新增一台受信设备时,新设备会生成自己的同步密钥对并向云端发出加入信任链的请求support.apple.com。已有的一台受信设备(通常是用户主动在其上同意新增设备)会验证该请求并通过 设备间安全信道 传输 DEK 副本给新设备support.apple.com。在此过程中,现有设备会利用新设备的公钥来加密封装 DEK,或双方通过椭圆曲线 Diffie-Hellman(ECDH)协商会话密钥来传递 DEK,从而确保只有目标新设备能解开密钥包装。苹果未公开具体用哪种算法封装,但业界常用方案包括 AES 密钥封装算法(AES-KW) 或 AES-GCM 算法 对会话密钥加密support.apple.comsupport.apple.com。可以推测,Apple 采用了符合 NIST 标准的 AES-256 算法对对称 DEK 进行二次加密包装,并结合设备的非对称密钥进行密钥交换/加密,以实现端到端的安全传递。
本地存储与保护:当设备接收到封装的 DEK 后,会在本地将其解密并安全保存于设备的 Keychain 中。所有 DEK 私钥仅存在于设备的安全隔区中,例如 iPhone 的密钥保存在 Data Protection 类钥匙串项下,并受 Secure Enclave 协处理器保护(访问需通过用户设备解锁)support.apple.com。这样设计保证即使设备遗失或被攻破,未解锁状态下设备上的 DEK 依然难以提取。总之,多设备环境下,每台受信设备都持有全局 DEK 副本,但始终通过端到端加密的方式同步与存储:传输过程中使用公钥加密/会话密钥,存储时依赖设备硬件密钥封装技术(如 Secure Enclave 提供的UID派生密钥)进一步加密,最大程度降低密钥泄露风险。
设备新增、移除与丢失场景下 DEK 和数据的生命周期
新设备加入: 当用户在新设备上登入 iCloud 并启用高级数据保护时,该设备无法直接访问云端受保护数据,需要首先加入信任链。加入流程包括:新设备生成自己的同步密钥对并将公钥提交给苹果云端(CloudKit)support.apple.com;苹果服务器将此请求传达给用户已有的一台受信设备上,提醒用户有新设备申请加入。用户在已有设备上批准请求(需输入密码或通过生物识别验证身份),之后已有设备会将新设备的公钥添加到信任链并再次用自己的私钥和账户密码派生密钥签署信任圈数据support.apple.com。随后,该已有设备通过上述安全信道,将全局 DEK 的加密副本传送给新设备support.apple.com。一旦新设备成功解密获得 DEK,它就加入了受信设备列表,可以像其他设备一样解密云端的端到端加密数据。整个过程确保只有获得用户明示批准的新设备才能获取 DEK support.apple.com。
设备移除与更换:当用户从 Apple ID 中移除某台设备,或设备被抹除/重置时,该设备将不再被视为信任链的一员。此时其他仍在线的受信设备会更新信任链状态,将该设备的身份从受信列表中剔除support.apple.com。需要强调的是,移除设备本身并不会导致全局 DEK 自动更改。被移除的设备虽曾持有 DEK 副本,但一旦不再受信,其无法从苹果服务器获取新的数据更新,而且由于设备已从账户移除或被抹掉,攻击者无法再借此解密云端后续的数据。苹果并未设定在每次设备变动时轮换密钥,这是出于实用性的考虑——频繁更换 DEK 将要求对云端大量数据重新加密,代价高昂。不过,若某台设备遗失且用户怀疑其本地密钥可能泄露,用户可以选择手动采取措施,例如从 iCloud 设置中移除此设备并重置高级数据保护(关闭再开启),从而生成新的 DEK,保护未来的数据安全。
云端数据影响: 当设备移除或失效时,云端已经加密的数据依旧由原来的 DEK 保护,并不会因为设备离开而重新加密。只要用户其他任一受信设备仍保存着该 DEK,便可继续访问此前的数据。被移除的设备由于缺失信任凭证,也无法再从服务器同步到后续新增或修改的任何机密数据(即使攻击者拥有其物理设备,由于密钥受 Secure Enclave 和设备密码保护,也难以提取support.apple.com)。因此,在多设备环境中,云端数据的可访问性取决于至少有一台受信设备存有对应 DEK。只要用户至少有一台设备或有效的恢复方式,数据就可解密使用;反之则数据陷于加密状态无法读取。
失去所有设备:高级数据保护要求用户在失去所有受信设备的极端情况下,借助预先设置的恢复机制取回 DEK。苹果强制要求启用该功能的用户提供至少一种账户恢复方法(例如指定恢复联系人或设置恢复密钥)support.apple.comsupport.apple.com。当用户所有设备均遗失或不可用时,只有通过这些恢复方式才能重获对数据的访问权。具体而言,如果用户提前设置了恢复密钥(一串随机生成的28位字符)并安全保存,那么此时用户可在新设备上登陆 Apple ID,并输入该恢复密钥来恢复数据。苹果服务器会将一份加密的 DEK 备份( escrow 记录 )下发到新设备,而新设备利用用户提供的恢复密钥将其解密,提取出全局 DEKsupport.apple.comsupport.apple.com。由于恢复密钥是由用户掌控、苹果不存储明文的要素,只有提供正确密钥的新设备才能解开 escrow 获得 DEK。在成功恢复后,新设备将重建信任链,并可以访问之前端到端加密的所有云端数据。
若用户选择的是恢复联系人,流程类似:用户联系预先设定的可信联系人,由联系人通过其苹果设备生成一个验证代码提供给用户。用户在新设备上输入该代码后,苹果同样将加密的 DEK 备份下发,新设备据此恢复密钥。整个恢复流程依然遵循端到端加密原则:苹果仅充当中转并验证权限,但并不知晓用户的实际 DEK 内容support.apple.com。
不可恢复的情况:如果用户既没有其他受信设备、又未设置任何恢复联系人或恢复密钥,那么全局 DEK 将无法找回,相应的云端数据也就永久处于加密不可读状态support.apple.com。苹果明确表示,若用户丢失所有设备且无恢复方式,公司无法帮助用户恢复这部分端到端加密的数据support.apple.com。这凸显了高级数据保护的一个权衡:安全性增强的同时,数据恢复的责任完全由用户自担。因此用户需谨慎管理受信设备和恢复选项,以避免陷入无法解密个人数据的境地。
DEK 安全性的密码学保障机制
苹果在高级数据保护与 iCloud 钥匙串架构中运用了多种密码学机制来保障 DEK 的机密性和完整性,包括密钥封装、密钥派生、硬件安全模块,以及严格的权限控制:
-
端到端加密与密钥层级化:如上所述,iCloud 采用分层密钥架构对数据加密。以 CloudKit 私有数据库为例,每位用户有一个顶层的 CloudKit 服务密钥对,其私钥用来保护下层对称密钥(如 Zone密钥、Record记录密钥等)
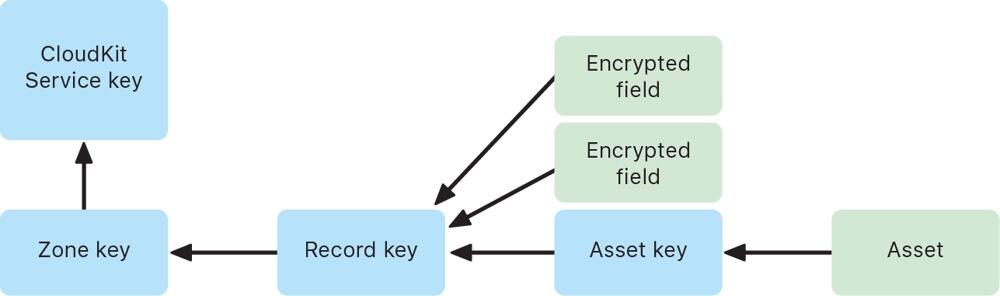 support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。
support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。 -
AES 密钥封装与封闭式硬件存储:苹果广泛采用了经验证的对称加密算法来封装和存储 DEK。传输过程中的 DEK(或下层对称密钥)通常通过 AES-256 算法加密封装后再上传support.apple.com。一种常用方法是 AES 密钥包装 (AES-KW),它专门用于用一个对称密钥安全地封装另一个密钥,确保密钥材料在传输中不暴露。与此同时,设备本地的 DEK 私钥会存储在受 Secure Enclave 保护的区域。Secure Enclave 为每台设备提供唯一的硬件 UID 密钥,仅用于解锁设备密钥袋和钥匙串项support.apple.com。也就是说, DEK 私钥本身可能被进一步用设备硬件密钥加密(这相当于在软件密钥之外又加了一道硬件锁)。只有当用户解锁设备并通过身份验证,操作系统才能调用 Secure Enclave 解封这些密钥用于加解密操作。通过AES-GCM 等对称加密结合Secure Enclave 硬件密钥封装,苹果确保 DEK 无论在云端传输还是本地存储,都始终处于加密状态,降低被截获或提取的风险support.apple.com。
-
椭圆曲线密码与密钥交换: 信任链中设备互认和密钥共享依赖椭圆曲线密码算法。每台设备的同步身份密钥对采用强大的 P-256 或 P-384 曲线support.apple.comsupport.apple.com。当新设备加入时,已有设备会利用椭圆曲线数字签名算法 (ECDSA) 对信任链数据签名校验,防止伪造support.apple.com。同时,在设备间传输 DEK 时,可能使用椭圆曲线 Diffie-Hellman (ECDH) 来建立共享密钥,加密传输内容。ECDH 可确保即使通信被窃听,攻击者无法推导出会话密钥,因而无法获取密钥内容。综上,非对称加密和密钥交换协议保证了只有合法设备才能参与密钥同步,新设备的引入需要现有设备用其私钥签名确认,杜绝中间人攻击或伪造信任链的可能。
-
密钥派生函数 (KDF):在某些步骤中,苹果使用了密钥派生函数强化密码。历史上,iCloud 钥匙串曾要求用户设置 iCloud 安全码时,将用户密码通过 PBKDF2 等KDF算法派生出密钥,用于签名和加密信任圈hackmag.comhackmag.com。即便在新的双重认证架构下,某些场景仍可能涉及KDF——例如恢复密钥或联系人代码很可能通过 KDF 转换为实际用于解密 escrow 密文的密钥材料。这些 KDF 算法引入高强度的盐值和大量迭代运算hackmag.com,增强了抗暴力破解能力,防止弱口令被攻击者猜测。总之,KDF 的应用确保从用户口令/恢复码到加密密钥的映射具有单向性和计算复杂度,进一步保护 DEK 相关流程的安全。
服务器无权获取明文 DEK 的保障
苹果的设计宗旨是在云端架起“盲墙”,确保服务器既无权也无实能接触用户 DEK 的明文,这也是实现“即使云端泄露,用户数据仍安全”的关键:
-
密钥仅存在于用户端: 开启高级数据保护后,所有主要 iCloud 数据类别的加密密钥仅存储于用户受信设备(或用户掌握的恢复载体)中,苹果服务器端不再保存这些密钥support.apple.com。文档明确指出,启用该功能后,苹果“无法读取或访问用户的服务密钥”support.apple.com。即在正常运行过程中,苹果的云服务器从未拥有解锁用户端到端加密数据所需的密钥。服务器所见到的只是由用户设备加密后的数据碎片,对其而言是不可解密的黑箱。
-
云端存储密文及加密元数据:iCloud 服务器虽然需要存储用户数据(如云照片、备忘录的加密内容),但这些内容均已由设备使用 DEK 加密完成。即便是为了提供某些功能,云端保留了少量未加密的元数据(如文件校验和用于重复数据消除),这些元数据也不包含可用于推导 DEK 的信息support.apple.comsupport.apple.com。苹果正在致力于将更多此类元数据也纳入端到端加密范围,以进一步减少明文暴露面support.apple.com。此外,CloudKit 框架要求开发者在模式中明确标记需要加密的字段,未标记的字段(例如排序用的时间戳)即便明文存储,亦不涉及敏感内容support.apple.com。由此,云服务器始终缺乏关于 DEK 或用户敏感数据的明文,一旦发生数据泄露或内部越权,攻击者拿到的也只是高强度加密下的乱码。
-
权限架构防范后门访问:苹果构建的信任链机制也防止了服务器假借授权来获取密钥的可能性。服务器不能私自添加受信设备或篡改信任链,因为每次信任链更新都需要现有设备的私钥签名以及(在老架构下)用户密码派生密钥的二次签名hackmag.comsupport.apple.com。苹果服务器既不持有用户设备私钥,也不知晓用户密码,因此无法伪造这些签名来诱导其他设备信任一个恶意设备。即使在双重认证体系下,服务器在设备加入流程中充当中继,并没有能力绕过用户批准直接将新设备植入圈内support.apple.comsupport.apple.com。这种架构等于为服务器访问用户密钥设置了密码学上的禁区。正如苹果安全白皮书所言,在最坏情形下如果用户丢失对 iCloud 钥匙串和其恢复机制的访问,那么相应的端到端加密数据苹果也无力恢复support.apple.com。苹果通过制度和技术结合,确保即便政府或机构要求提供用户数据,由于公司本身并无解密能力,只能交出加密的内容。
综上所述,Apple 高级数据保护下,全局数据加密密钥的生成由用户设备掌控,借助 iCloud 钥匙串信任链在多设备间安全同步。无论是在设备增加、移除还是用户失去设备的情况下,密钥和数据的生命周期管理均以用户掌控为中心:只要用户保有至少一个密钥载体(设备或恢复方式),数据即可解密使用;反之苹果也无法绕过用户获取密钥明文support.apple.com。苹果通过成熟的加密算法(AES-KW、ECDH 等)、硬件支持(Secure Enclave)、密钥分层与派生策略,实现了“零信任”云存储:服务器对用户密钥一无所知,从而使用户云端数据获得前所未有的保密性提升。
附录
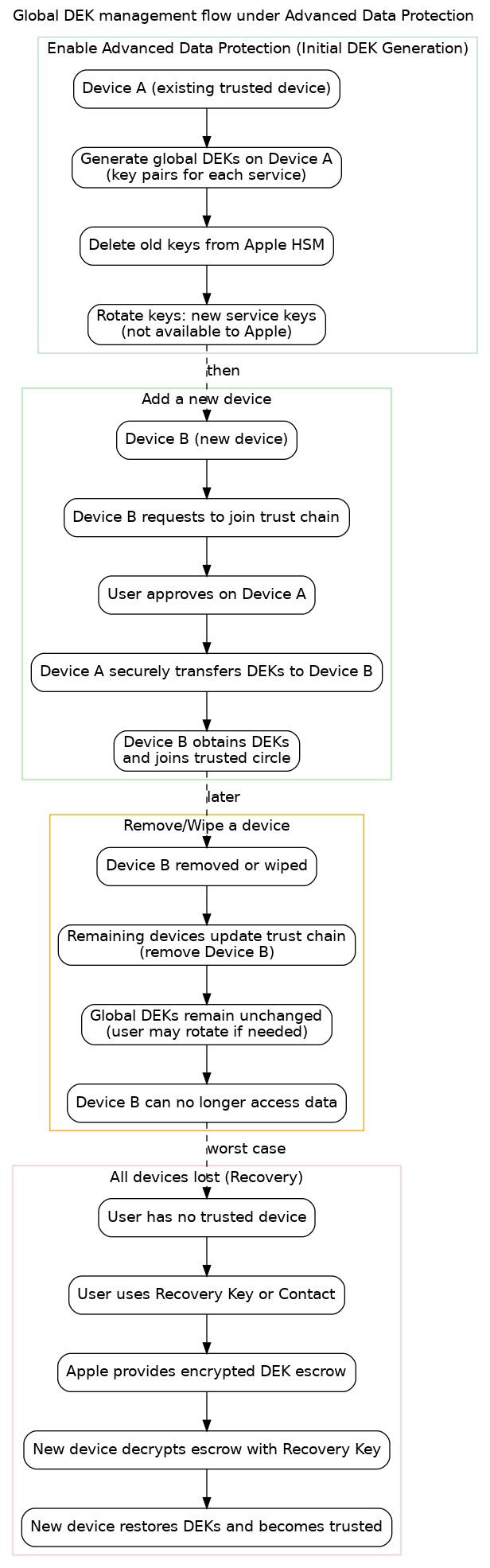 图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。
图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。 -
-
 @ b99efe77:f3de3616
2025-05-18 02:40:36
@ b99efe77:f3de3616
2025-05-18 02:40:36🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ b99efe77:f3de3616
2025-05-18 02:36:11
@ b99efe77:f3de3616
2025-05-18 02:36:11🚦Traffic Light Control System🚦1111111112
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 9ca447d2:fbf5a36d
2025-05-18 11:16:36
@ 9ca447d2:fbf5a36d
2025-05-18 11:16:36Bahrain-based Al Abraaj Restaurants Group has made history by becoming the first publicly-traded company in the Middle East to add bitcoin to its corporate treasury. This is a major step forward for regional bitcoin adoption.
On May 15, 2025, Al Abraaj Restaurants Group, a well-known restaurant chain listed on the Bahrain Bourse, announced it had bought 5 bitcoin (BTC) as part of a new treasury strategy. This makes the company the first in Bahrain, the GCC and the Middle East to officially hold bitcoin as a reserve asset.
Al Abraaj adds bitcoin to its treasury — Zawya
This is a growing trend globally where companies are treating bitcoin not just as an investment but as a long-term store of value. Major companies like Strategy, Tesla and Metaplanet have already done this — and now Al Abraaj is following suit.
Metaplanet recently added 1,241 BTC to its treasury, boosting the company’s holdings above El Salvador’s.
Related: Metaplanet Overtakes El Salvador in Bitcoin Holdings After $126M Purchase
“Our initiative towards becoming a Bitcoin Treasury Company reflects our forward-thinking approach and dedication to maximizing shareholder value,” said Abdulla Isa, Chairman of the Bitcoin Treasury Committee at Al Abraaj.
Al Abraaj’s move is largely inspired by Michael Saylor, Executive Chairman of Strategy, the world’s largest corporate holder of bitcoin. Saylor’s strategy of allocating billions to bitcoin has set a model that other companies — now including Al Abraaj — are following.
A photo shared by the company even showed a meeting between an Al Abraaj representative and Saylor, with the company calling itself the “MicroStrategy of the Middle East”.
“We believe that Bitcoin will play a pivotal role in the future of finance, and we are excited to be at the forefront of this transformation in the Kingdom of Bahrain,” Isa added.
To support its bitcoin initiative, Al Abraaj has partnered with 10X Capital, a New York-based investment firm that specializes in digital assets.
10X Capital has a strong track record in bitcoin treasury strategies, and recently advised Nakamoto Holdings on a $710 million deal — the largest of its kind.
With 10X’s help, Al Abraaj looks to raise more capital and increase its bitcoin holdings over time to maximize bitcoin-per-share for its investors. The company will also develop Sharia-compliant financial instruments so Islamic investors can get exposure to bitcoin in a halal way.
“Bahrain continues to be a leader in the Middle East in Bitcoin adoption,” said Hans Thomas, CEO of 10X Capital. He noted, with a combined GDP of $2.2 trillion and over $6 trillion in sovereign wealth, the GCC now has its first publicly listed bitcoin treasury company.
This is not just a first for Al Abraaj — it’s a first for the region. Bahrain has been positioning itself as a fintech hub and Al Abraaj’s move will encourage more non-fintech companies in the region to look into bitcoin.
The company said the decision was made after thorough due diligence and is in line with the regulations set by the Central Bank of Bahrain (CBB). Al Abraaj will be fully compliant with all digital asset transaction rules, including transparency, security and governance.
A special Bitcoin Committee has been formed to oversee the treasury strategy. It includes experienced bitcoin investors, financial experts and portfolio managers who will manage risk, monitor market conditions and ensure best practices in custody and disclosure.
The initial purchase was 5 BTC, but Al Abraaj sees this as just the beginning. The company stated that there are plans in motion to allocate a significant portion of their treasury into bitcoin over time.
According to the company’s reports, Al Abraaj is financially sound with $12.5 million in EBITDA in 2024. This strong financial foundation gives the company the confidence to explore new strategies like bitcoin investment.
-
 @ f11e91c5:59a0b04a
2025-04-30 07:52:21
@ f11e91c5:59a0b04a
2025-04-30 07:52:21!!!2022-07-07に書かれた記事です。
暗号通貨とかでお弁当売ってます 11:30〜14:00ぐらいでやってます
◆住所 木曜日・東京都渋谷区宇田川町41 (アベマタワーの下らへん)
◆お値段
Monacoin 3.9mona
Bitzeny 390zny
Bitcoin 3900sats (#lightningNetwork)
Ethereum 0.0039Ether(#zkSync)
39=thank you. (円を基準にしてません)
最近は週に一回になりました。 他の日はキッチンカーの現場を探したり色々してます。 東京都内で平日ランチ出店出来そうな場所があればぜひご連絡を!
 写真はNFCタグです。
スマホにウォレットがあればタッチして3900satsで決済出来ます。
正直こんな怪しい手書きのNFCタグなんて絶対にビットコイナーは触りたくも無いだろうなと思いますが、これでも良いんだぜというメッセージです。
写真はNFCタグです。
スマホにウォレットがあればタッチして3900satsで決済出来ます。
正直こんな怪しい手書きのNFCタグなんて絶対にビットコイナーは触りたくも無いだろうなと思いますが、これでも良いんだぜというメッセージです。今までbtcpayのposでしたが速度を追求してこれに変更しました。 たまに上手くいかないですがそしたら渋々POS出すので温かい目でよろしくお願いします。
ノードを建てたり決済したりで1年経ちました。 最近も少しずつノードを建てる方が増えてるみたいで本当凄いですねUmbrel 大体の人がルーティングに果敢に挑むのを見つつ 奥さんに土下座しながら費用を捻出する弱小の私は決済の利便性を全開で振り切るしか無いので応援よろしくお願いします。
あえて あえて言うのであれば、ルーティングも楽しいですけど やはり本当の意味での即時決済や相手を選んでチャネルを繋げる楽しさもあるよとお伝えしたいっ!! 決済を受け入れないと分からない所ですが 承認がいらない時点で画期的です。
QRでもタッチでも金額指定でも入力でも もうやりようには出来てしまうし進化が恐ろしく早いので1番利用の多いpaypayの手数料(事業者側のね)を考えたらビットコイン凄いじゃない!と叫びたくなる。 が、やはり税制面や価格の変動(うちはBTC固定だけども)ウォレットの操作や普及率を考えるとまぁ難しい所もあるんですかね。
それでも継続的に沢山の人が色んな活動をしてるので私も何か出来ることがあれば 今後も奥さんに土下座しながら頑張って行きたいと思います。
(Originally posted 2022-07-07)
I sell bento lunches for cryptocurrency. We’re open roughly 11:30 a.m. – 2:00 p.m. Address Thursdays – 41 Udagawa-chō, Shibuya-ku, Tokyo (around the base of Abema Tower)
Prices Coin Price Note Monacoin 3.9 MONA
Bitzeny 390 ZNY Bitcoin 3,900 sats (Lightning Network)
Ethereum 0.0039 ETH (zkSync) “39” sounds like “thank you” in Japanese. Prices aren’t pegged to yen.These days I’m open only once a week. On other days I’m out scouting new spots for the kitchen-car. If you know weekday-lunch locations inside Tokyo where I could set up, please let me know!
The photo shows an NFC tag. If your phone has a Lightning wallet, just tap and pay 3,900 sats. I admit this hand-written NFC tag looks shady—any self-respecting Bitcoiner probably wouldn’t want to tap it—but the point is: even this works!
I used to run a BTCPay POS, but I switched to this setup for speed. Sometimes the tap payment fails; if that happens I reluctantly pull out the old POS. Thanks for your patience.
It’s been one year since I spun up a node and started accepting Lightning payments. So many people are now running their own nodes—Umbrel really is amazing. While the big players bravely chase routing fees, I’m a tiny operator scraping together funds while begging my wife for forgiveness, so I’m all-in on maximising payment convenience. Your support means a lot!
If I may add: routing is fun, but instant, trust-minimised payments and the thrill of choosing whom to open channels with are just as exciting. You’ll only understand once you start accepting payments yourself—zero-confirmation settlement really is revolutionary.
QR codes, NFC taps, fixed amounts, manual entry… the possibilities keep multiplying, and the pace of innovation is scary fast. When I compare it to the merchant fees on Japan’s most-used service, PayPay, I want to shout: “Bitcoin is incredible!” Sure, taxes, price volatility (my shop is BTC-denominated, though), wallet UX, and adoption hurdles are still pain points.
Even so, lots of people keep building cool stuff, so I’ll keep doing what I can—still on my knees to my wife, but moving forward!
-
 @ b99efe77:f3de3616
2025-05-18 02:35:54
@ b99efe77:f3de3616
2025-05-18 02:35:54🚦Traffic Light Control System🚦111111
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 41fa852b:af7b7706
2025-05-18 09:33:15
@ 41fa852b:af7b7706
2025-05-18 09:33:15> "Only he who attempts the absurd is capable of achieving the impossible."—Miguel de Unamuno
It’s a busy week with the Bitcoin Ireland conference and Pizza Day celebrations in Thames Ditton and Bristol.
Support your local Bitcoin communities by attending as many of this week’s meetups and events as possible.
Let’s Go!
Upcoming Bitcoin Meetups
Happening this week…
-
Lincolnshire Bitcoin: Lincolnshire Bitcoin meets on the second Monday of each month at 7:30 PM in the Treaty of Commerce, Lincoln. Open to all, from OG’s to newcomers. This month on the 19th. 🍺
-
Bitcoin Surrey: This months Surrey meetup features special guest Freddie New, co-founder of Bitcoin Policy UK at The Bourne Club, 12 Frensham Rd GU9 8HB 18:00 with the talk starting at 19:00. 🍺🎤
-
Newcastle upon Tyne Bitcoin Meetup: The next Newcastle meetup is on Tuesday 20th May at Kabin @ Kabannas NE1 6UQ. 6:30 PM. 🍺
-
Bitcoin Glasgow: Bitcoin Glasgow meet every 3rd Wednesday of the month and this month will be at The Maltman, 59–61 Renfield Street at 18:00 to 20:00. 🍻
-
Bitcoinology @ Cyphermunk House: This will be primarily a social event. Attendees are encouraged to bring their burning questions to address as many as possible. Everyone is welcome, whether to share knowledge as an expert or to learn as a student. Bitcoinology will provide structure to ensure a shared learning experience that’s both engaging and enjoyable. 👨🏻🏫👨🏼🎓
-
Shropshire Bitcoin: On the 21st, the Shropshire crew will be meeting at the Admiral Benbow in Shrewsbury. 19:00 - 23:00. 🍺
-
Bitcoin Pizza Day at Thames Ditton: Celebrate Bitcoin Pizza Day with the Surrey Bitcoiners on May 22nd, 2025, in Thames Ditton, where local venues will be accepting Bitcoin for food and drinks in honour of the first real-world Bitcoin transaction. Just 20 minutes from London Waterloo, it’s the perfect chance to enjoy a slice, connect with fellow Bitcoiners, and support businesses embracing sound money. 🍕
-
Bitcoin Bristol - Pizza Day: If Thames Ditton is a bit too far, don’t worry. Bristol will also be celebrating Bitcoin Pizza Day in style on Thursday, May 22nd at 18:15 at Stable Pizza, Harbourside. This informal gathering offers a relaxed setting to chat over drinks in a lively public bar with no table reservations—just drop by. It’s a great chance to discuss Bitcoin news, ideas, and developments while meeting others in the local scene. Everyone is welcome, from curious newcomers to seasoned OGs, and all questions are encouraged. For help finding the group on the night, join the Telegram chat at t.me/BitcoinBristol. 🍕
-
The Satoshi Society - Southampton: Join a friendly group of bitcoiners at The Maritimo Lounge, Ocean Village on Friday 23rd May for food and a Bitcoin chat at 18:00. 🍺 🍴
-
Into The Valueverse: The first UK live music event, built on top of Bitcoin. Into the Valueverse is a celebration of artists brought together through Bitcoin. Performing live are Longy, a raw and rebellious voice from Southend blending rock, folk, and punk; Joe Martin, a heartfelt singer-songwriter inspired by folk and Americana greats; and Nathan Abbot, an Essex-based artist known for his soulful voice and powerful storytelling. The event takes place at The Fickle Pickle Club, 228 London Road, Westcliff-on-Sea, on Friday 23rd May, 2025. Doors open at 19:30, show starts at 20:00, and it’s for ages 18 and over. 🎶🎸🎤
-
Bitcoin Ireland Conference: Set to take place on Saturday, May 24, at The Green Isle Hotel in Dublin. This community-driven event aims to connect Irish Bitcoin enthusiasts, promote Bitcoin-friendly businesses, and educate the public about the potential of Bitcoin. Attendees can expect a day filled with insightful talks, networking opportunities, and discussions on various aspects of Bitcoin, including its impact on finance, energy, and society. The conference will feature a diverse lineup of speakers, including Daniel Prince, Knut Svanholm, Francis Pouliot, and British HODL, among others. Whether you’re a seasoned Bitcoiner or just curious about the technology, the Bitcoin Ireland Conference offers a platform to learn, share, and engage with the growing Bitcoin community in Ireland. 🎤🫂
-
Bitcoin Walk - Edinburgh: Every Saturday they walk around Arthur’s Seat in this historic city. Join them at 12 pm to chat about all things Bitcoin and keep fit. 🚶🏽♂️🚶🏼♀️🚶🏻
New Businesses Accepting Bitcoin
This week we have…
-
McCann Bespoke Tailors: Founded by Neil McCann in 2002, has grown from a South London garage into a leading name in British tailoring. Known for its craftsmanship and high-profile partnerships–from the Savoy Hotel to Premier League clubs–the brand now operates a flagship store on Lime Street with a private bar and dedicated consultation space. McCann Bespoke is now accepting Bitcoin. 👔
-
Moradok Siam in Romsey: Bun is a specialist in deep tissue massage, known for helping those suffering from persistent muscular aches and pains; particularly in the back, shoulders, and neck. Drawing on years of experience, she works with precision to identify problem areas and applies targeted techniques to relieve tension and restore movement. Her treatments aren’t for the faint-hearted, but they offer real results. Many clients are referred by local doctors after conventional treatments like injections and medication have failed. For lasting relief, regular appointments are strongly recommended. 💆🏻♂️
Upcoming Special Events
These events aren’t happening next week, but they’re important to add to your calendar now as tickets are selling fast.
Bloom Festival 2025: Takes place 31 May – 1 June at Cypher Munk House, London. This open-source celebration brings together developers, artists, and tinkerers to explore tech, culture, and Bitcoin.
🎤 Talks & Panels
Topics include:
-
Open-source innovation
-
The Bitcoin whitepaper
-
Decentralized publishing
-
Bitcoin in UK education
🛠️ Workshops
Get hands-on with:
-
Off-grid mesh networks
-
DIY Bitcoin signing devices
-
Censorship-resistant publishing
-
Creative coding with open tools
🎨 Creative & Cultural
-
Collaborative art & music
-
Acoustic performances
-
Bitcoin-inspired exhibitions
🛍️ The Souk
-
Open-source hardware
-
Seed storage gear
-
Prints and handmade goods

Children of Riddim Festival - Bitcoin Stage: This is shaping up to be one of the biggest music festivals with Bitcoin vibes in the world.
Around 150 DJs, artists, and speakers will perform over four days, from 12–16 June, in Hemel Hempstead. A dedicated stage, the Barn of Freedom, will spotlight Bitcoin culture, education, and unstoppable apps on the Nostr protocol–alongside music, talks, and much more.
Support for the Barn of Freedom stage can be given via geyser.fund, where both ticket purchases and donations are welcome. One-day and four-day passes are available, and on-site camping is included.
Confirmed names include Joe Bryan, Metamick (Geyser Fund), Roger9000, Angor, MadMunky, Huxley, and many more.
The Bitcoin Beach Retreat: An annual Bitcoin-only gathering held at a scenic coastal campsite in North Wales. Celebrating its fifth year in 2025, the retreat offers a relaxed, community-driven alternative to traditional conferences. From July 11–14, up to 120 Bitcoiners will come together to share knowledge, enjoy beachside BBQs, and strengthen their networks under the stars. With no pre-booked speakers, the event thrives on peer-led workshops and spontaneous discussions, fostering genuine connections among attendees. Emphasising local engagement, the retreat directs the majority of its funds into the surrounding community, with 42% of expenses paid in Bitcoin last year. Whether attending solo or with family, attendees can expect a welcoming environment dedicated to sound money and shared values.
Get Involved
-
Volunteer: Passionate about merchant adoption? Reach out to Bridge2Bitcoin on Twitter or website.
-
Start a Meetup: Want to launch a Bitcoin meetup? We’ll support you. Contact us on Twitter or just reply to this email.
-
Contribute to BTCMaps: Help maintain this key Bitcoin resource—no coding skills needed. Update a UK area.
-
Telegram: Join our Channel for UK meetup updates
-
Feedback: Reply to this email with ideas and suggestions.
This week’s sponsors is…
Get out and support the meetups where you can, visit Bitcoin Events UK for more info on each meetup and to find your closest on the interactive map.
Stay tuned for more updates next week!
Simon.
-
-
 @ 78b3c1ed:5033eea9
2025-04-29 04:04:19
@ 78b3c1ed:5033eea9
2025-04-29 04:04:19Umbrel Core-lightning(以下CLNと略す)を運用するにあたり役に立ちそうなノウハウやメモを随時投稿します。
・configファイルを用意する Umbrelのアプリとして必要な設定はdocker-compose.ymlで指定されている。 それ以外の設定をしたい場合configファイルに入れると便利。 configファイルの置き場所は /home/umbrel/umbrel/app-data/core-lightning/data/lightningd ここにtouch configとでもやってファイルをつくる。
cd /home/umbrel/umbrel/app-data/core-lightning/data/lightningd touch config以下内容をひな型として使ってみてください。 行頭に#があるとコメント行になります。つまり.iniフォーマット。 /home/umbrel/umbrel/app-data/core-lightning/data/lightningd/config ```[General options]
[Bitcoin control options]
[Lightning daemon options]
[Lightning node customization options]
[Lightning channel and HTLC options]
[Payment control options]
[Networking options]
[Lightning Plugins]
[Experimental Options]
``` configに設定できる内容は以下を参照 https://lightning.readthedocs.io/lightningd-config.5.html セクションを意味する[]があるけれどもこれは私(tanakei)が意図的に見やすく区別しやすくするために付けただけ。これら行の#は外さない。
・configの設定をCLNに反映させる appスクリプトでCLNを再起動すると反映することができる。 configを書き換えただけでは反映されない。
cd /home/umbrel/umbrel/scripts ./app restart core-lightning・ログをファイルに出力させる
以下の場所でtouch log.txtとしてlog.txtファイルを作る。 /home/umbrel/umbrel/app-data/core-lightning/data/lightningd
cd /home/umbrel/umbrel/app-data/core-lightning/data/lightningd touch log.txt次にconfigの[Lightning daemon options]セクションにlog-fileを追加する。 ```[Lightning daemon options]
log-file=/data/.lightning/log.txt ``` ※Dockerによって/home/umbrel/umbrel/app-data/core-lightning/data/lightningd は /data/.lightning として使われている。
・addrとbind-addrの違い どちらも着信用のインターフェースとポートの設定。addrは指定したホストIPアドレス:ポート番号をノードURIに含めて公開する(node_announcementのuris)。bind-addrは公開しない。
・実験的機能のLN Offerを有効にする configの[Experimental Options]セクションに以下を追加する。 ```
[Experimental Options]
experimental-onion-messages experimental-offers ``` ※ v24.08でexperimental-onion-messageは廃止されデフォルト有効であり、上記設定の追加は不要になりました。 ※ v21.11.1 では experimental-offersは廃止されデフォルト有効であり、上記設定の追加は不要になりました。 もう実験扱いじゃなくなったのね...
・完全にTorでの発信オンリーにする UmbrelはなぜかCLNの発信をClearnetとTorのハイブリッドを許している。それは always-use-proxy=true の設定がないから。(LNDは発着信Torのみなのに) なのでこの設定をconfigに追加してCLNも発着進Torのみにする。 ```
[Networking options]
always-use-proxy=true ```
・任意のニーモニックからhsm_secretを作る CLNのhsm_secretはLNDのwallet.dbのようなもの。ノードで使う様々な鍵のマスター鍵となる。Umbrel CLNはこのhsm_secretファイルを自動生成したものを使い、これをバックアップするためのニーモニックを表示するとかそういう機能はない。自分で作って控えてあるニーモニックでhsm_secretを作ってしまえばこのファイルが壊れてもオンチェーン資金は復旧はできる。
1.CLNインストール後、dockerコンテナに入る
docker exec -it core-lightning_lightningd_1 bash2.lightning-hsmtoolコマンドを使って独自hsm_secretを作る ``` cd data/.lightning/bitcoin lightning-hsmtool generatehsm my-hsm_secret・上記コマンドを実行するとニーモニックの言語、ニーモニック、パスフレーズの入力を催促される。 Select your language: 0) English (en) 1) Spanish (es) 2) French (fr) 3) Italian (it) 4) Japanese (jp) 5) Chinese Simplified (zhs) 6) Chinese Traditional (zht) Select [0-7]: 0 ※定番の英単語なら0を入力 Introduce your BIP39 word list separated by space (at least 12 words): <ニーモニックを入力する> Warning: remember that different passphrases yield different bitcoin wallets. If left empty, no password is used (echo is disabled). Enter your passphrase: <パスフレーズを入力する> ※パスフレーズ不要ならそのままエンターキーを押す。 New hsm_secret file created at my-hsm_secret Use the
encryptcommand to encrypt the BIP32 seed if neededコンテナから抜ける exit
3.appスクリプトでCLNを止めて、独自hsm_secret以外を削除 ※【重要】いままで使っていたhsm_secretを削除する。もしチャネル残高、ウォレット残高があるならチャネルを閉じて資金を退避すること。自己責任!cd ~/umbrel/scripts/ ./app stop core-lightningcd ~/umbrel/app-data/core-lightning/data/lightningd/bitcoin rm gossip_store hsm_secret lightningd.sqlite3 lightning-rpc mv my-hsm_secret hsm_secret
4.appスクリプトでCLNを再開するcd ~/umbrel/scripts/ ./app start core-lightning ```【補記】 hsm_secret作成につかうニーモニックはBIP39で、LNDのAezeedと違って自分が作成されたブロック高さというものを含んでいない。新規でなくて復元して使う場合は作成されたブロック高さからブロックチェーンをrescanする必要がある。 configの1行目にrescanオプションを付けてCLNをリスタートする。 ``` // 特定のブロック高さを指定する場合はマイナス記号をつける rescan=-756000
// 現在のブロック高さから指定ブロック分さかのぼった高さからrescanする rescan=10000 ※現在の高さが760,000なら10000指定だと750,000からrescan ```
・clnrestについて core-lightningでREST APIを利用したい場合、別途c-lightning-restを用意する必要があった。v23.8から標準でclnrestというプラグインがついてくる。pythonで書かれていて、ソースからビルドした場合はビルド完了後にpip installでインストールする。elementsproject/lightningdのDockerイメージではインストール済みになっている。 (v25.02からgithubからバイナリをダウンロードしてきた場合はpip install不要になったようだ) このclnrestを使うにはcreaterunesコマンドでruneというLNDのマカロンのようなものを作成する必要がある。アプリ側でこのruneとREST APIを叩いてcore-lightningへアクセスすることになる。 自分が良く使っているLNbitsやスマホアプリZeus walletはclnrestを使う。まだclnrestに対応していないアプリもあるので留意されたし。
・Emergency recoverについて LNDのSCBのようなもの。ファイル名はemergency.recover チャネルを開くと更新される。 hsm_secretとこのファイルだけを置いてCLNを開始すると自動でこのファイルから強制クローズするための情報が読み出されてDLPで相手から強制クローズするような仕組み。この機能はv0.12から使える。
動作確認してみた所、LNDのSCBに比べるとかなり使いづらい。 1. CLNがTor発信だとチャネルパートナーと接続できない。 Clearnet発信できても相手がTorのみノードならTor発信せざるを得ない。 相手と通信できなければ資金回収できない。 2. 相手がLNDだとなぜか強制クローズされない。相手がCLNならできる。
つまり、自分と相手がClearnetノードでかつ相手もCLNならば Emergency recoverで強制クローズして資金回収できる。こんな条件の厳しい復旧方法がマジで役に立つのか?
v0.11以降ならばLNDのchannel.dbに相当するlightningd.sqlite3をプライマリ・セカンダリDBと冗長化できるので、セカンダリDBをNFSで保存すればUmbrelのストレージが壊れてもセカンダリDBで復旧できる。そのためemergerncy.recoverを使う必要がないと思われる。
・LN offer(BOLT#12)ついて 使いたいなら 1.publicチャネルを開く publicチャネルを開けばチャネルとノードの情報(channel_announcement, node_announcement)が他ノードに伝わる。送金したい相手がこの情報を元に経路探索する。 2.その後しばらく待つ CLNノードを立てたばかりだと経路探索するに十分なチャネルとノードの情報が揃ってない。せめて1日は待つ。
LNURLの場合インボイスをhttpsで取得するが、OfferはLN経由で取得する。そのためにチャネルとノードの情報が必要。privateチャネルばかりのノードはチャネル情報もそうだがノード情報も出さない。 Offerで使えるBlind pathという機能なら中間ノードIDを宛先ノードとすることが可能で、これならチャネルとノード情報を公開しなくても受けとれるのだがCLNは対応してない模様(2025年1月現在) CLNでOfferで受け取るにはチャネルとノード情報を公開する必要がある。そのためpublicチャネルを開く。公開されていれば良いのでTorでもOK。クリアネットで待ち受けは必須ではない。
・hsm_sercretとニーモニック lightning-hsmtoolを使うとニーモニックからhsm_secretを作れる。ニーモニックからシードを作ると64バイト。これはニーモニックおよびソルトにパスフレーズをPBKDF2(HMAC-SHA512を2048回)にかけると512ビット(64バイト)のシードができる。しかしhsm_secretは32バイト。CLNでは64バイトの最初の32バイトをhsm_secretとして利用しているみたい。 このhsm_secretにHMAC-SHA512をかけて512ビットとした値がウォレットのマスター鍵となる。なのでhsm_secret自体がBIP-32でいうマスターシードそのものではない。 sparrow walletにCLNのウォレットを復元したい場合は lightning-hsmtool dumponchaindescriptors --show-secrets
とやってディスクリプターウォレットを出力。出力内容にマスター鍵(xprv~)があるので、これをインポートする。導出パス設定はm/0とする。sparrowが残りを補完してm/0/0/0, m/0/0/1とやってくれる。 <おまけ> configファイルのサンプル。Umbrelを使わない場合は以下のサンプルが役に立つはず。上記のelementsproject/lightningdならば/root/.lightningに任意のディレクトリをマウントしてそのディレクトリにconfigを置く。 ```
[General options]
不可逆なDBアップグレードを許可しない
database-upgrade=false
[Bitcoin control options]
network=bitcoin bitcoin-rpcconnect=
bitcoin-rpcport= bitcoin-rpcuser= bitcoin-rpcpassword= [Lightning daemon options]
postgresを使う場合
wallet=postgres://USER:PASSWORD@HOST:PORT/DB_NAME
bookkeeper-db=postgres://USER:PASSWORD@HOST:PORT/DB_NAME
sqlite3を使う場合。デフォルトはこちらで以下の設定が無くても~/.lightning/bitconに自動で作成される。
wallet=sqlite3:///home/USERNAME/.lightning/bitcoin/lightningd.sqlite3
bookkeeper-db=sqlite3:///home/USERNAME/.lightning/bitcoin/accounts.sqlite3
ログファイルは自動で作成されない
log-file=/home/USERNAME/.lightning/lightningd-log
log-level=debug
[Lightning node customization options]
alias=
rgb= 固定手数料。ミリサトシで指定。
fee-base=1000000
変動手数料。ppmで指定。
fee-per-satoshi=0
最小チャネルキャパシティ(sats)
min-capacity-sat=100000
HTLC最少額。ミリサトシで指定。
htlc-minimum-msat=1000
[Lightning channel and HTLC options]
large-channels # v23.11よりデフォルトでラージチャネルが有効。
チャネル開設まで6承認
funding-confirms=6
着信できるHTLCの数。開いたら変更できない。1~483 (デフォルトは 30) の範囲にする必要があります
max-concurrent-htlcs=INTEGER
アンカーチャネルを閉じるためにウォレットに保持しておく資金。デフォルトは 25,000sat
チャネルを"忘れる(forget)"するまではリザーブされる模様。forgetはチャネル閉じてから100ブロック後
min-emergency-msat=10000000
[Cleanup control options]
autoclean-cycle=3600 autoclean-succeededforwards-age=0 autoclean-failedforwards-age=0 autoclean-succeededpays-age=0 autoclean-failedpays-age=0 autoclean-paidinvoices-age=0 autoclean-expiredinvoices-age=0
[Payment control options]
disable-mpp
[Networking options]
bind-addrだとアナウンスしない。
bind-addr=0.0.0.0:9375
tor
proxy=
: always-use-proxy=true Torの制御ポート。addr=statictor だとhidden serviceをノードURIとして公開する。
addr=statictor:
: tor-service-password= experimental-websocket-portは廃止された。bind-addr=ws:が代替。
bind-addr=ws:
:2106 clnrestプラグイン, REST API
clnrest-host=0.0.0.0 clnrest-port=3010 clnrest-protocol=http
v24.11よりgrpcはデフォルト有効
grpc-host=0.0.0.0 grpc-port=9736
[Lightning Plugins]
[Experimental Options]
experimental-onion-messages # v24.08で廃止。デフォルト有効
experimental-offers # v24.11.1で廃止。デフォルト有効
流動性広告からチャネルを開くときにexperimental-dual-fundが必要らしい。
experimental-dual-fund
experimental-splicing
experimental-peer-storage
```
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 78b3c1ed:5033eea9
2025-04-27 01:48:48
@ 78b3c1ed:5033eea9
2025-04-27 01:48:48※スポットライトから移植した古い記事です。参考程度に。
これを参考にしてUmbrelのBitcoin Nodeをカスタムsignetノードにする。 以下メモ書きご容赦。備忘録程度に書き留めました。
メインネットとは共存できない。Bitcoinに依存する全てのアプリを削除しなければならない。よって実験機に導入すべき。
<手順>
1.Umbrel Bitcoin Nodeアプリのadvance settingでsignetを選択。
2.CLI appスクリプトでbitcoinを止める。
cd umbrel/scripts ./app stop bitcoin3.bitcoin.conf, umbrel-bitcoin.conf以外を削除ディレクトリの場所は ~/umbrel/app-data/bitcoin/data/bitcoin4.umbrel-bitcoin.confをsu権限で編集。末尾にsignetchallengeを追加。 ``` [signet] bind=0.0.0.0:8333 bind=10.21.21.8:8334=onion51,21,<公開鍵>,51,ae
signetchallenge=5121<公開鍵>51ae
5.appスクリプトでbitcoinを開始。cd ~/umbrel/scripts ./app start bitcoin ``` 6.適当にディレクトリを作りgithubからbitcoindのソースをクローン。7.bitcoindのバイナリをダウンロード、bitcoin-cliおよびbitcoin-utilを~/.local/binに置く。6.のソースからビルドしても良い。ビルド方法は自分で調べて。
8.bitcondにマイニング用のウォレットを作成 ``` alias bcli='docker exec -it bitcoin_bitcoind_1 bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>'
ウォレットを作る。
bcli createwallet "mining" false true "" false false
秘密鍵をインポート
bcli importprivkey "<秘密鍵>"
RPCパスワードは以下で確認cat ~/umbrel/.env | grep BITCOIN_RPC_PASS9.ソースにあるbitcoin/contrib/signet/minerスクリプトを使ってマイニングcd <ダウンロードしたディレクトリ>/bitcoin/contrib/signet難易度の算出
./miner \ --cli="bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>" calibrate \ --grind-cmd="bitcoin-util grind" --seconds 30 ★私の環境で30秒指定したら nbits=1d4271e7 と算出された。実際にこれで動かすと2分30になるけど...
ジェネシスブロック生成
./miner \ --cli="bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>" generate \ --address <ビットコインアドレス> \ --grind-cmd="bitcoin-util grind" --nbits=1d4271e7 \ --set-block-time=$(date +%s)
継続的にマイニング
./miner \ --cli="bitcoin-cli -signet -rpcconnect=10.21.21.8 -rpcport=8332 -rpcuser=umbrel -rpcpassword=<パスワード>" generate \ --address <ビットコインアドレス> \ --grind-cmd="bitcoin-util grind" --nbits=1d4271e7 \ --ongoing ``` ここまでやればカスタムsignetでビットコインノードが稼働する。
-
 @ 0000065e:9b5b4c75
2025-05-17 21:19:58
@ 0000065e:9b5b4c75
2025-05-17 21:19:58En mayo de 2024, el Juzgado de lo Mercantil nº 2 de Bilbao dictó sentencia por la que se declaraba la nulidad de la marca 4.046.141 que reproducía el logotipo diseñado y publicado por el usuario anónimo “bitboy” en el foro bitcointalk.org y con el que popularmente se identifica Bitcoin.
El titular de la marca recurrió la sentencia y ahora la Audiencia Provincial de Vizcaya confirma íntegramente la resolución del Juzgado y, por tanto, la nulidad de la marca, considerando que la marca se registró de mala fe y que infringía los derechos de propiedad intelectual sobre el diseño registrado como marca.
En cuanto a la mala fe, la Audiencia Provincial destaca que la marca registrada estaba basada “en un diseño preexistente de la comunidad de internet”, como acredita la prueba documental obrante en autos y particularmente el informe pericial presentado donde se indica que “término "Bitcoin" identifica la tecnología que permite el almacenamiento y transmisión de valor, puesta en conocimiento público por "Satoshi Nakamoto" en el "White paper" del 31 de octubre de 2008. El dominio bitcoin.org se registró en agosto de 2008 de manera anónima”. A lo que añadir que tanto el logotipo como su combinación con el término "bitcoin" fueron creados por un usuario del foro Bitcointalk.org el 1 de noviembre de 2010. Y que los derechos sobre estas imágenes fueron cedidos a la comunidad bajo una licencia Creative Commons de dominio público.”
Concluye así la sentencia con que “a fecha del registro del signo distintivo por el demandante, "bitcoin" ya era conocido y el demandante registró una obra ajena, protegida por la normativa de propiedad intelectual y que forma parte del dominio público.”
La Audiencia considera que “como se ha acreditado, quien creó el logotipo lo cedió a la comunidad para un uso libre y sin restricción, prohibiendo expresamente que cualquiera se apropiara del logotipo para fines comerciales. Por ello, el reproche a la parte apelante es de mala fe ya que ha actuado con abuso de confianza al registrar el logotipo para sus fines comerciales, aprovechándose de la reputación ganada por el creador del logotipo. El apelante no es el creador del logotipo ni se le autorizó su uso y actúa en contra de las prácticas leales en el mercado."
En cuanto a la infracción de los derechos de propiedad intelectual, la Audiencia señala que “la sentencia de instancia acertadamente, considera que el logotipo registrado como marca es una creación ajena al apelante y que está protegida por la Ley de Propiedad Intelectual, y que su registro incurre en la causa de nulidad del artículo 52 en relación con el 9.1.c) de la Ley de Marcas… El juzgador de lo mercantil efectúa un análisis probatorio acorde con la prueba obrante en las actuaciones y conforme a la normativa, con cita de la relevante sentencia de la AP de Madrid ( SAP de Madrid, secc. 28.a, de 1 de septiembre de 2022) en relación con el “creative commons” y hemos de concluir como se hace en la instancia “ el derecho de autor nace de la creación, no de un registro, llevado a cabo”.
El equipo jurídico de Bit2Me, liderado y coordinado por Javier Maestre, con el apoyo del área de compliance y legal de la compañía y el despacho de abogados DataBitLaw, ha llevado el caso en representación de Bit2Me, para obtener una resolución judicial que contribuye a la protección de los signos distintivos que identifican a Bitcoin, a fin de que nadie pueda hacer un uso exclusivo de los mismos, como defiende la iniciativa de bitboydefense.
-
 @ 58537364:705b4b85
2025-05-18 08:20:04
@ 58537364:705b4b85
2025-05-18 08:20:04มีคำหนึ่งในพุทธศาสนาที่เราอาจจะคุ้นหู แต่ว่าความเข้าใจอาจจะไม่ตรงกับความหมายในพุทธศาสนา นั่นคือคำว่า อธิปไตย
เวลาเรานึกถึงอธิปไตย ก็นึกไปถึงเรื่องของการเมือง ระบอบการปกครอง เช่น ประชาธิปไตย แต่อธิปไตยในพุทธศาสนาไม่ใช่เป็นเรื่องของระบอบการปกครอง แต่เป็นเรื่องของการให้คุณค่าให้ความสำคัญ
อธิปไตยก็แปลว่าการถือเอาเป็นใหญ่ เอาอะไรเป็นใหญ่ ก็มี 3 ประการใหญ่ ๆ อันแรกคือธรรมาธิปไตย คือการเอาธรรมะเป็นใหญ่ อันที่ 2 คืออัตตาธิปไตย การถือเอาตัวเองหรืออัตตาเป็นใหญ่ และ 3 โลกาธิปไตย ถือเอาคนหมู่มากเป็นใหญ่ ความหมายนี้ก็คือว่าไม่ได้มีความเห็นเป็นของตัวเอง แต่ว่าทำไปตามความเห็นของคนส่วนใหญ่ ที่เรียกว่าโลก เป็นต้น
แต่ว่าหลัก ๆ ก็มีอยู่ 2 อย่าง ที่เราควรจะใส่ใจและก็ทำความเข้าใจให้ถูกต้อง นั่นคือ ธรรมาธิปไตยกับอัตตาธิปไตย
การถือธรรมเป็นใหญ่ ความหมายคือเอาความถูกต้องเป็นใหญ่ เวลาเราทำงานทำการหรือเราใช้ชีวิต ถ้าเราถือธรรมเป็นใหญ่หรือธรรมาธิปไตย เราก็จะตั้งตัวอยู่ในศีลในธรรม ไม่เบียดเบียนผู้อื่น เพราะเห็นแก่ความถูกต้อง แต่ถ้าเราเอาตัวเองเป็นใหญ่หรืออัตตาธิปไตย มันก็คือการเอาประโยชน์ของตัวเองเป็นใหญ่ ไม่สนใจว่าความถูกต้องหรือระเบียบกฎเกณฑ์จะเป็นอย่างไร ถ้าเราถือตัวเองเป็นใหญ่ การที่เราจะอยู่ในศีลธรรมก็ยาก เพราะว่าเอาความต้องการของตัวเองเป็นหลัก ซึ่งส่วนใหญ่ก็เป็นเรื่องของกิเลสนั่นแหละ หรือความเห็นแก่ตัว
อัตตาธิปไตยในความหมายที่แย่คือการเห็นแก่ตัว ส่วนธรรมาธิปไตยเห็นแก่ธรรมะ เห็นแก่ความถูกต้อง หรือถ้าพูดง่าย ๆ คือว่าธรรมาธิปไตยคือการเอาถูกความเป็นใหญ่ ส่วนอัตตาธิปไตยคือเอาความถูกใจเป็นใหญ่
อันนี้เราก็มาพิจารณาดูง่าย ๆ ในการดำเนินชีวิตของคนเรา ในแต่ละวันเราเอาอะไรเป็นใหญ่ อย่างเช่นเวลากินอาหาร ถ้าเราเอาความถูกต้องเป็นใหญ่ หรือธรรมาธิปไตย เราก็จะกินอาหารที่เป็นประโยชน์ต่อสุขภาพ เพื่อทำให้ร่างกายแข็งแรง มีกำลังวังชา เพื่อที่จะได้ทำกิจการงานต่าง ๆ ได้
แต่ถ้าเอาความถูกใจเป็นใหญ่ เราก็จะกินเพราะว่ามันอร่อย เอารสชาติเป็นใหญ่ ถึงแม้ว่ามันจะไม่เป็นประโยชน์ต่อสุขภาพ แต่มันอร่อย มันหวาน มันเปรี้ยว มันเผ็ด มันเค็ม หรือว่ามันสีสวยน่ากิน ทั้ง ๆ ที่มันอาจจะเจือไปด้วยสารพิษที่เป็นอันตราย
หลายคนก็รู้ว่ากินอาหารที่มันเต็มไปด้วยไขมัน อุดมไปด้วยน้ำตาล เป็นโทษต่อสุขภาพ แต่ก็ห้ามใจไม่ได้ กินมาก ๆ เข้า สุดท้ายก็เป็นโรคหัวใจ โรคเบาหวาน ไตวาย หรือบางทีถ้ากินอาหารประเภทที่มันเป็นของดิบ เช่น ปลาดิบ มีพยาธิใบไม้ในตับ ก็เกิดเป็นมะเร็งในตับ หลายคนก็รู้ว่ากินอาหารแบบนี้ ทำให้เกิดโรคเป็นมะเร็งในตับ รู้ว่ามันไม่ถูกต้องแต่ก็กิน เพราะมันถูกใจ
หรือเวลาเราเรียนหนังสือ ถ้าความถูกต้อง เราก็ต้องเรียนด้วยความขยันหมั่นเพียร ต้องมีความซื่อสัตย์สุจริต เวลาทำการบ้าน หรือเวลาเข้าห้องสอบ แต่ถ้าเราเอาความถูกใจเป็นใหญ่ เรียนบ้างไม่เรียนบ้าง บางวิชาฉันไม่ชอบฉันก็ไม่เรียน เวลาทำการบ้านก็ไปลอกจากเพื่อน หรือว่าไปตัดแปะมาจากกูเกิ้ลหรือวิกิพีเดีย เวลาสอบก็ทุจริต แม้รู้ว่าไม่ถูกต้อง แต่มันถูกใจ คือมันสะดวก ง่าย สบาย
เวลาทำงานถ้าเราเอาความถูกต้องเป็นใหญ่ เราก็จะทำงานด้วยความรับผิดชอบ แม้ว่าเป็นงานที่เราไม่ชอบ แต่เมื่อเรามีหน้าที่ เราก็ต้องพยายามทำให้ดีที่สุด เพราะเป็นความรับผิดชอบของเรา แต่ถ้าเอาความถูกใจ งานนี้ฉันไม่ชอบ ฉันก็ไม่ทำ ต่อเมื่อเป็นงานที่ฉันชอบ ฉันจึงจะทำ
หรือถ้าเป็นงานที่ฉันไม่ได้อะไร ฉันไม่ทำ จะทำก็ต่อเมื่อเป็นงานที่ได้ผลประโยชน์ เวลาจะทำอะไรก็จะถามว่าทำแล้วฉันจะได้อะไร อันนี้ก็คือเอาความถูกใจเป็นหลัก หรือเอาความถูกใจเป็นใหญ่ในเวลาทำงาน
เวลาใช้ข้าวของ เช่นโทรศัพท์มือถือ ถามตัวเราเองว่าเราใช้ความถูกต้องหรือความถูกใจ ถ้าใช้ความถูกต้องเป็นใหญ่ ก็จะใช้โทรศัพท์เพื่อติดต่องานการ ทำกิจธุระ หาความรู้ เช็คข้อมูล อาจจะดูหนังฟังเพลงบ้าง ก็ให้เวลากับมันพอสมควร ไม่ใช่หมกมุ่นอยู่กับมัน โดยไม่เป็นอันทำอะไร งานการก็ไม่สนใจ ก้มหน้าดูแต่โทรศัพท์ ใช้ดูหนังฟังเพลง หรือบางทีหนักกว่านั้น ใช้เพื่อเล่นพนันออนไลน์ หรือเล่นเกมออนไลน์ วันหนึ่งหลายชั่วโมง การใช้โทรศัพท์มือถือแบบนี้ ก็เรียกว่าไม่ได้เอาความถูกต้องเป็นใหญ่ แต่เอาความถูกใจเป็นใหญ่
ฉะนั้นลองพิจารณาดูเรื่องการใช้ชีวิตของคนเรา รวมทั้งความสัมพันธ์กับผู้คน เราใช้อะไรเป็นใหญ่ เอาความถูกต้องเป็นใหญ่ หรือเอาความถูกใจเป็นใหญ่ เวลาคบเพื่อน เวลามีเรื่องที่ต้องเกี่ยวข้องกับผู้คน ถ้าเราเอาความถูกต้องเป็นใหญ่ เราก็จะคำนึงถึงความรู้สึกของอีกฝ่ายหนึ่ง เราจะไม่คิดถึงแต่จะเบียดเบียน เอาเปรียบ ต้องมีความเสียสละ แล้วก็รู้จักอดกลั้น ไม่ทำตามอารมณ์
แต่ถ้าเอาความถูกใจเป็นใหญ่ ก็เรียกว่าไม่สนใจว่าคนอื่น เขาจะรู้สึกอย่างไร เอาเปรียบได้ก็เอาเปรียบ ไม่พอใจอะไรก็โวยวาย เรียกว่าขาดน้ำใจ แล้วก็ขาดความรับผิดชอบ มันเป็นเส้นแบ่งได้เลยในเรื่องคน ในเรื่องของพฤติกรรม ในเรื่องของการกระทำ ว่าเราใช้ความถูกต้องหรือความถูกใจ
ถ้าเราเอาความถูกต้องเป็นใหญ่ ชีวิตก็มีโอกาสที่จะเจริญก้าวหน้า อยู่ในศีลในธรรม ตั้งมั่นในความดี แต่ถ้าเราเอาความถูกใจเป็นใหญ่ ก็มีโอกาสที่จะตกต่ำย่ำแย่ เพราะสุดท้ายก็กลายเป็นคนเห็นแก่ตัว หรือว่าตกเป็นทาสของกิเลส อยากกินอะไรก็กิน อยากทำอะไรก็ทำ ไม่ได้สนใจส่วนรวม
เวลามาอยู่วัดก็เหมือนกัน ถ้าเอาความถูกต้องเป็นใหญ่ เราก็จะปฏิบัติตามกฎระเบียบ แม้บางอย่างเราอาจจะต้องฝืนใจทำ เพราะว่าเราเป็นคนตื่นสาย แต่ว่าเราจำเป็นต้องตื่นเช้ามาทำวัตร เพราะว่ามันเป็นระเบียบ มันเป็นข้อวัตร เป็นกติกา เวลามีการทำกิจส่วนรวมก็ไปร่วมช่วยทำ
แต่ถ้าเราเอาความถูกใจเป็นใหญ่ มาบ้างไม่มาบ้าง ทำวัตร เอาความอยากของตัวเองเป็นหลัก ไม่อยากมาก็ไม่มา หรือว่าไม่อยากตื่นก็ไม่ตื่น งานที่เป็นของส่วนรวม ฉันไม่อยากทำฉันก็ไม่ทำ อันนี้ก็ทำให้ชีวิตเราย่ำแย่ไป
แต่ที่จริงแล้วถ้าเราแยกแยะความถูกต้อง ความถูกใจเป็น ก็จะทำให้เราสามารถที่จะใช้ชีวิตไปในทางที่ถูกต้องได้ แต่บางครั้งมันก็ไม่ง่ายที่เราจะแยกแยะได้ชัดเจน ระหว่างความถูกต้องกับความถูกใจ เพราะบางครั้งกิเลสมันก็ฉลาด มันจะอ้างความถูกต้องเฉพาะเวลาที่ถูกใจ แต่ถ้าหากว่าความถูกต้องยามใดไม่ถูกใจฉัน ฉันก็ไม่สนใจ
อย่างเช่นเวลาทำงาน สิ้นปีก็มีโบนัส ถ้าหากว่าฉันได้โบนัส แต่ถ้ารู้ว่าคนอื่นได้โบนัสมากกว่าฉัน เช่นฉันได้ 50,000 แต่อีกคนได้ 70,000 หรือแสนหนึ่ง ก็จะไม่พอใจ ก็จะอ้างว่าไม่ถูกต้อง ไม่เป็นธรรม ความเป็นธรรมคืออะไร ความถูกต้องคืออะไร ก็คือต้องได้เท่ากัน ก็อาจจะเรียกร้อง อาจจะประท้วง อาจจะโวยวายว่ามันต้องเป็นธรรม คือต้องได้เท่ากัน ถึงจะถูกต้อง
แต่ถ้าหากว่าตัวเองได้มากกว่า ตัวเองได้แสน แต่ว่าคนอื่นเขาได้ 50,000, 70,000 เงียบเลย ไม่พูดสักคำเลยว่ามันไม่ถูกต้อง มันไม่เป็นธรรม เพราะอะไร เพราะว่าฉันได้มากกว่า คราวนี้ฉันได้มากกว่า ก็ถือว่าเป็นเรื่องที่ถูกใจฉันแล้ว ถึงตอนนี้ก็ทิ้งเรื่องความถูกต้องไป แต่ถ้าเราเอาความถูกต้องเป็นใหญ่ แม้ว่าจะมีเงินหรือได้เงินมากกว่าคนอื่น มันก็ไม่ถูกต้องอยู่นั่นเอง ก็ต้องทำให้เกิดความถูกต้องขึ้นมา คือว่าต้องได้เท่าคนอื่น
หลายคนเรียกร้องความถูกต้อง เรียกร้องความเป็นธรรม บ่อยครั้งเลยเพราะว่าตัวเองสูญเสียผลประโยชน์ หรือว่าไม่ได้ประโยชน์เท่ากับคนอื่น ถ้าหากว่าตัวเองได้เกิดน้อยกว่าคนอื่น จะเรียกร้องความเป็นธรรม เรียกร้องความถูกต้อง แต่ถ้าหากว่าตัวเองได้มากกว่าคนอื่น ความถูกต้องก็ลืมไปเลย อันนี้แหละนะเรียกว่าอ้างความถูกต้องต่อเมื่อมันถูกใจฉัน ทั้งที่ถ้าถูกต้องแล้วฉันได้เท่าคนอื่น แต่กลับดีหากว่าฉันได้มากกว่าคนอื่น แล้วหากความถูกต้องหมายถึงว่าฉันต้องได้น้อยลง ลดลงมาจากแสนให้เหลือ 70,000 เท่ากับคนอื่น ฉันไม่เอาแล้ว
อันนี้ก็เป็นสิ่งที่เราพบอยู่บ่อย ๆ อ้างความถูกต้องต่อเมื่อมันถูกใจ แต่ถ้ามันไม่ถูกใจฉันเมื่อไหร่ ก็ไม่อ้างความถูกต้องแล้ว ลืมไปเลย อันนี้ก็ต้องระมัดระวัง เพราะบางครั้งกิเลสมันก็ฉลาด มันก็อ้างความถูกต้อง เพื่อสนองผลประโยชน์ของมัน และบางทีเราก็นิยามความถูกต้องแปรผันไป ขึ้นอยู่กับความถูกใจ
ความถูกต้องหรือความเป็นธรรม มันก็มองได้หลายแง่ และตรงนี้แหละ เป็นโอกาสที่จะทำให้ตัวกิเลสมันมาเป็นตัวกำหนด ว่าอย่างไหนเรียกว่าเป็นความถูกต้อง
อย่างเช่นหมู่บ้านหนึ่ง เมื่อสัก 30-40 ปีก่อน สมัยที่ยังไม่มีอบต. ในหมู่บ้านนั้นมีปั๊มน้ำ ที่ใช้แบบคันโยก เป็นปั๊มน้ำของหมู่บ้าน มันเกิดเสียขึ้นมา นักศึกษาที่เป็นพัฒนากรประจำหมู่บ้าน เขาก็เสนอว่าควรจะเก็บเงินทุกหลังคาเลยหลังคาละ 10 บาท เพื่อเป็นค่าซ่อมปั๊ม
ปรากฏว่าชาวบ้านหลายคนไม่ยอม บอกว่าบ้านฉันอยู่ไกลจากปั๊มน้ำ ฉันไม่ค่อยได้ใช้หรอก บ้านไหนที่ใช้ปั๊มมากกว่า เพราะอยู่ใกล้ปั๊ม ควรจะเสียมากกว่า ส่วนบ้านไหนที่อยู่ไกลใช้น้อย ก็ควรจะเสียน้อย แทนที่จะเสีย 10 บาท ก็เสีย 5 บาท เสียเท่ากันนี่ถือว่าไม่เป็นธรรม ตกลงก็เป็นอันว่าต้องเสียไม่เท่ากัน
แต่หนึ่งเดือนต่อมาในหมู่บ้าน มีคนเอาผ้าห่มมาแจก เพราะว่ามันใกล้ฤดูหนาว เอามาถวายวัด หลวงพ่อเจ้าอาวาสท่านก็ปรึกษามัคทายก เพราะว่าผ้าห่มมันไม่พอที่จะแจกให้ชาวบ้านทุกครัวเรือนเท่ากัน มัคทายกก็เสนอว่าบ้านไหนที่ช่วยส่วนรวมได้ 2 ผืน บ้านไหนที่ไม่ค่อยช่วยส่วนรวมได้ 1 ผืน
พอประกาศอย่างนี้เข้า ชาวบ้านไม่พอใจ บอกว่าไม่เป็นธรรม เป็นธรรมคืออะไร เป็นธรรมคือต้องได้เท่ากัน ก็แปลกนะ เวลาจ่ายเงิน ต้องจ่ายไม่เท่ากัน ถึงจะเป็นธรรม แต่เวลาพอได้ผ้าห่มหรือแจกผ้าห่ม ต้องได้เท่ากันถึงจะเป็นธรรม
อันนี้แปลว่าอะไร แปลว่าความเป็นธรรมหรือความถูกต้องนี่มันไม่แน่นอน มันแปรผันขึ้นอยู่กับความถูกใจ จ่ายเท่ากัน หลายคนไม่ถูกใจ ควรจะจ่ายน้อยกว่า จ่ายไม่เท่ากันจึงจะเรียกว่าเป็นธรรม แต่ถึงเวลาได้ ต้องได้เท่ากันจึงจะเป็นธรรม
ถ้าเราพิจารณาดูก็จะพบว่า นี่มันเป็นการนิยามคำว่าเป็นธรรม หรือความถูกต้องโดยอาศัยความถูกใจ ถึงเวลาได้ ต้องได้เท่ากันจึงจะถูกใจ ถ้าได้ไม่เท่ากัน ไม่ถูกใจ ก็ถือว่าไม่เป็นธรรม แต่เวลาจ่าย ต้องจ่ายไม่เท่ากันจึงจะถูกต้อง ฉันต้องจ่ายน้อยกว่า เพราะบ้านฉันอยู่ไกล อย่างนี้เรียกว่าเป็นธรรม
ฉะนั้นความเป็นธรรม ถ้าเราไม่ระวัง มันก็เป็นข้ออ้างเพื่อสนองกิเลส เพื่อสนองความถูกใจ ถ้าเราดูให้ดี ๆ ความถูกต้อง ความถูกใจ แม้ว่าความหมายจะต่างกัน แต่ถ้าไม่ระวัง มันก็กลายเป็นเรื่องเดียวกันได้ ก็คือว่าอันไหนถูกใจจึงเรียกว่าถูกต้อง อันไหนไม่ถูกใจก็เรียกว่าไม่ถูกต้อง
และอีกอย่างหนึ่งคือแม้เราจะมีความชัดเจนว่าอย่างนี้คือความถูกต้อง แต่ก็ต้องระวัง อย่าไปยึดมั่นถือมั่นกับมันมาก เพราะถ้าเราไปยึดมั่นถือมั่นกับความถูกต้องเมื่อไหร่ พอเจอใครทำอะไรไม่ถูกต้อง กลายเป็นไม่ถูกใจไปเลย
อย่างที่เคยเล่า ศีลจาริณี บวชใหม่ ไม่รู้ธรรมเนียม ยืนกินน้ำ แม่ชีเดินผ่านมาเห็นคาตาเลย อย่างนี้ไม่ถูกต้อง แต่ว่าไปยึดกับความถูกต้องมากไป พอเจอความไม่ถูกต้องขึ้นมา โกรธนะ ทุบหลังศีลจาริณีเลย อันนี้เรียกว่าเป็นเพราะยึดมั่นความถูกต้องมาก ยึดมั่นกับระเบียบมาก พอยึดมั่นกับระเบียบหรือความถูกต้อง พอเจอความไม่ถูกต้อง หรือใครทำอะไรไม่ถูกต้อง ก็จะโกรธ
หรือว่าที่วัดก็มีระเบียบ เวลาฟังธรรมต้องปิดโทรศัพท์มือถือ อันนี้คือความถูกต้องที่ควรปฏิบัติร่วมกัน แต่เกิดมีโยมคนหนึ่งลืมปิดโทรศัพท์มือถือ แล้วบังเอิญมีคนโทรเข้ามา เสียงก็ดังกลางศาลาเลย ขณะที่เจ้าอาวาสกำลังเทศน์อยู่ นี่เป็นความไม่ถูกต้องแท้ ๆ เลย ถ้ายึดมั่นกับความถูกต้องมาก เวลาเจอความไม่ถูกต้องแบบนี้ก็โกรธ
โกรธแล้วเป็นอย่างไร ก็ตะโกนด่าเลย เจ้าอาวาสก็ตะโกนด่าเลย กำลังเทศน์อยู่ดีๆ เปลี่ยนโหมดเลยนะ เป็นการด่าแทน ด่าเจ้าของโทรศัพท์ที่ลืมปิดโทรศัพท์ อันนี้เรียกว่าพอเจอความไม่ถูกต้องนี่ มันเกิดไม่ถูกใจขึ้นมา พอไม่ถูกใจแล้วกิเลสมันก็พร้อมที่จะเล่นงาน พร้อมที่จะโวยวาย พร้อมที่จะพูด หรือพร้อมที่จะกระทำอะไรก็ตามด้วยอำนาจของโทสะ ด้วยอำนาจของกิเลส ซึ่งเป็นเรื่องของอัตตาธิปไตย
ฉะนั้นเราต้องระวัง ขณะที่เรายึดมั่นในความถูกต้อง ถ้าเรายึดมั่นมากไป พอเจอใครทำอะไรไม่ถูกต้องขึ้นมา ความไม่ถูกต้องจะกลายเป็นความไม่ถูกใจทันทีเลย ทั้งๆ ที่ดูเผินๆ ไม่ถูกต้องกับไม่ถูกใจนี่มันห่างกันนะ มันไกลกันมาก
เช่นเดียวกับความถูกต้อง ความถูกใจ บางทีมันก็ไกลกันมาก แต่ในบางครั้งบางคราว ถ้าไม่รู้ทันมัน มันกลายเป็นเรื่องเดียวกันไปเลย คือถ้าไม่ถูกต้องเมื่อไหร่ ก็ไม่ถูกใจเมื่อนั้น หรือจะเป็นสิ่งที่ถูกต้อง ก็ต่อเมื่อมันถูกใจ ถ้าอันไหนไม่ถูกใจ ก็ไม่ถูกต้องไป
อันนี้มันต้องใช้สติพิจารณา การที่เรารู้ว่าอะไรถูก อะไรผิด เป็นสิ่งที่ดี และการที่เราปฏิบัติตามความถูกต้อง ก็เป็นสิ่งที่ดี เรียกว่ามีธรรมาธิปไตย แต่ถ้าเรายึดมั่นในความถูกต้องมากไป มันก็ง่ายมากเลยนะ ที่เวลาเจอใครทำอะไรไม่ถูกต้อง ความไม่ถูกต้องก็กลายเป็นความไม่ถูกใจ หรือกระตุ้นให้เกิดความไม่ถูกใจทันที
แล้วบางทีก็ไม่รู้ตัวนะ ก็ยังคิดว่าฉันทำสิ่งที่ถูกต้อง แต่ที่จริงแล้วสิ่งที่ทำไปมันถูกใจต่างหาก แล้วมันก็เกินเลยความถูกต้องไป เพราะว่าไปทุบหลังคนอื่นนี่มันจะถูกต้องได้อย่างไร หรือว่าไปตะโกนด่ากลางศาลาในขณะที่ขาดสติ หรือทำไปด้วยความโกรธ จะเป็นความถูกต้องได้อย่างไร มันก็เป็นเรื่องละเอียดอ่อน ความถูกต้องไม่ใช่ว่ามันจะกลายเป็นสิ่งตรงข้ามกับความถูกใจ
ถ้าเราไม่ระวัง ความยึดมั่นถือมั่น มันก็จะทำให้ความถูกต้องกับความถูกใจ กลายเป็นอันเดียวกัน แล้วก็ทำให้เกิดความผิดพลาด หรือเกิดความเสียหายขึ้น
หลายคนก็ทำสิ่งที่ไม่ถูกต้องเพื่อพิทักษ์ความถูกต้อง อันนี้มีเยอะเลย ที่เป็นข่าวก็คือว่าไปฆ่าคนนั้นคนนี้เพื่อรักษาความถูกต้อง ไม่ว่าเป็นความถูกต้องทางการเมือง ความถูกต้องทางศาสนา
อย่างพวกที่เป็นพวกก่อการร้าย หลายคนเขาก็คิดว่าเขาทำเพื่อพระเจ้า เขาทำเพื่อพิทักษ์ความถูกต้องทางศาสนา แต่ว่าสิ่งที่เขาทำ มันกลายเป็นความไม่ถูกต้องไปเสียแล้ว ทำไปด้วยอำนาจของกิเลส ตัวเองเป็นคนตัดสินว่าใครจะอยู่ใครจะไป ใครที่คิดไม่เหมือนฉัน ก็ต้องถูกกำจัดออกไปจากโลกนี้ เพราะมันเป็นคนที่คิดไม่ถูกต้อง ปฏิบัติไม่ถูกต้อง
ที่จริงก็เป็นเพียงแค่เห็นต่างจากตัวเองเท่านั้น แต่พอเจอคนที่เห็นต่าง ก็เปลี่ยนจากความไม่ถูกใจ กลายเป็นข้ออ้างว่าเขาทำสิ่งที่ไม่ถูกต้อง เพราะฉะนั้นก็สมควรกำจัดออกไปจากโลกนี้
อันนี้เป็นสิ่งที่เราเห็นมากขึ้นเรื่อยๆ ที่เป็นข่าว แล้วมันไม่ใช่เพราะเรื่องศาสนาอย่างเดียว เรื่องการเมือง เรื่องวัฒนธรรม ก็มีความถูกต้องของมัน แต่ถ้าไปยึดความถูกต้องมากไป ใครที่ปฏิบัติไม่ถูกต้องในสายตาของเรา มันก็กลายเป็นสิ่งที่กระตุ้นความไม่ถูกใจ ทำให้เกิดความโกรธ ทำให้เกิดข้ออ้างในการที่จะจัดการ ทำร้าย หรือว่าสังหาร
ฉะนั้นต้องระวังมากทีเดียว การทำความไม่ถูกต้อง ในนามของความถูกต้อง ก็กลายเป็นว่าทำไปด้วยอำนาจของกิเลส แทนที่จะเป็นธรรมาธิปไตย ก็กลายเป็นอัตตาธิปไตยไป.
https://youtu.be/nvGHQUvjvOE
พระไพศาล วิสาโล วัดป่าสุคะโต 4 กันยายน 2565 ขอขอบคุณ Nonglak Trongselsat
-
 @ 005bc4de:ef11e1a2
2025-05-17 13:40:23
@ 005bc4de:ef11e1a2
2025-05-17 13:40:23Bitcoin, sats, bits, numbers, and perceptions
Quick background
In December 2024 John Carvalho proposed BIP 21Q titled "Redefinition of the Bitcoin Unit to the Base Denomination." His point: the word "bitcoin" should not refer to the 21 million bitcoins we hear about, but to what we currently call "sats", the "base" unit of bitcoin. There are 2.1 quadrillion sats. So, instead of saying there are 21 million bitcoin, BIP 21Q suggests saying there are 2.1 quadrillion.
There'd be absolutely zero change to Bitcoin, the protocol, with this BIP (unlike the OP_CAT or more current OP_RETURN debates). This is just a movement to get people to change the way they talk about and refer to "bitcoin." BIP 21Q is just a rewording, a rephrasing, a rebranding, a rethinking.
Since
Since then, there has been discussion. I'll admit it's interesting to talk about, but I've never thought much of it. My take has been, and frankly still is: this too will pass. I hadn't heard or thought of this in a couple of months. Until...
In the past couple of days though, like a campfire that has been slowly dying down, a sudden rush of wind has fanned the embers and the flames have sparked upward. As best I can tell, that wind came out of the mouth (or typing) of Jack Dorsey (Twitter founder, Square/Block CEO, billionaire, you know Jack) when he put this note out.
Watch the vid on YouTube.
The video makes some good points, both against and in favor of BIP 21Q. Quickly, Grok summarized the arguments for and against, below:

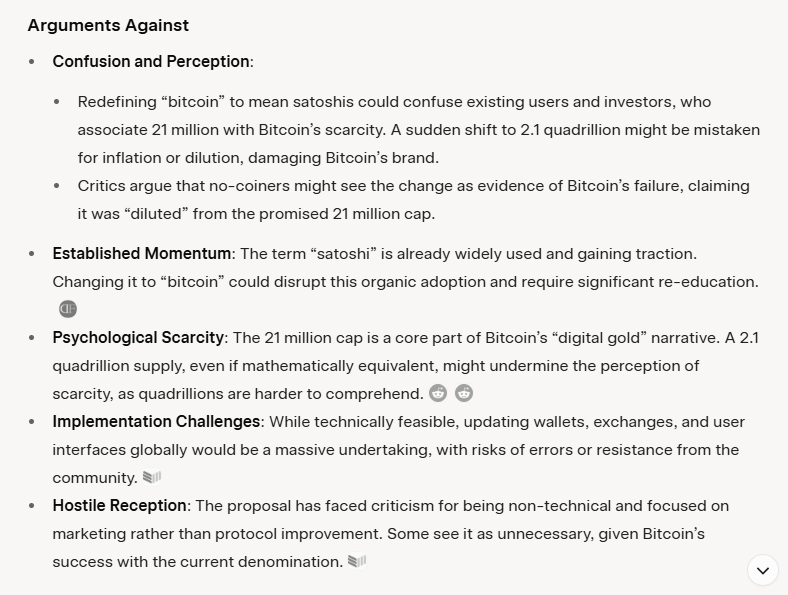
Today, I even read chatter about a middle ground compromise to use "bits" as the base unit. In other words, don't use "sats" but use "bits." I guess the idea is that a bitcoin can stay one of 21 million, but "bits," which sounds like little bitcoins, can be the 2.1 quadrillion. "Oh brother," I thought, even more confusion. We've been through this back in the 20-teens with bits, ubits, and mbits. This was a main reason I made the Satoshi Bitcoin Converter because it was confusing! I'm happy we were past all this, but then...it's back!
Just for kicks, you can fool around with the old SBC version 7 and find out how confusing it is.
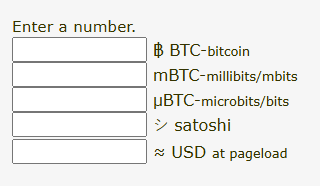
One of the arguments in the video is that the BoardwalkCash.com folks have adopted "bitcoin" as their base unit. Boardwalk Cash is a cashu/ecash (and Lightning) web app with the intention of making spending and receiving small, coffee-sized payments easy.
Notice the bitcoin B after the zero, not "sats" or a satoshi symbol, like the one I proposed: シ 😃
Below, I sent 21 sats (bitcoins?) from a different ecash/cashu wallet. And, boom, there they appear in Boardwalk Cash. Notice how it appears as 21₿, as 21 bitcoin. Then, when I click it, it shows $0.02 USD, two pennies.
I didn't actually send 21 what-we-think-of-today bitcoins, worth $2.16 million. I sent two US pennies worth.
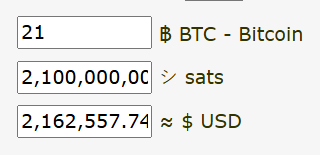
By the way, if you've never messed around with ecash/cashu and wish to try it out, get a wallet and I'll send you a few sats (bitcoins?) as ecash to see how easy it is. These images are from Boardwalkcash.com which is very clean, however I use Cashu.me.
And so...
And so, this is the main argument against, in my view: possible confusion. The other issue would be the changeover by things like exchanges or maybe even smart contracts that bridge BTC to other chains. Having worked on my little converter app, I know that it can be easy to make a decimal mistake in the code and throw everything off. I'm certain that, should we move to 2.1 quadrillion bitcoins, somebody will foul up an interface or back end which might cause a big problem, maybe some big losses.
Two things here:
On the more technical side, the changing of names and code on exchanges or smart contracts, it would almost be better if there was a hard-and-fast, set changeover date, like there was with Y2K. There is a clear before-and-after, B.C. and A.D. date. Call it, "BQ" and "AQ", before and after quadrillion. 😂 If there was a date/time where everything was 21M "bitcoin" to 2.1Q "bitcoin", that would force the issue.
However, there is not such a date or time, nor will there be...recall that bitcoin is decentralized, no CEO here. If this 2.1Q change actually happens, the reality is that it will be a rolling, gradual, thing. It will be case by case, app by app, exchange by exchange. And some won't make the change at all. This lends back to the confusion situation.
Secondly, on the human perception side, this actually concerns me less. We can change human perception. It takes some time, but human perception and thinking is very plastic and can definitely be molded. Heaven knows the examples of how this has been used the wrong way in history, umm, anything like this go on in World War II?
Quick case studies of changing perception:
Standard Oil (John D. Rockefeller's company) was essentially a monopoly and was broken up by the U.S., remember that from history class? They had a multitude of sub-brands, one of which was "Esso", get it?, S.O., Standard Oil? They wanted to move away from ties to Standard Oil, at least perception-wise, and wanted to consolidate all their sub-brands. They moved to "Exxon" with a marketing campaign. The marketing types were brilliant. They understood that there is a time thing involved. Unlike the Y2K hard date above, they knew that human perception, as malleable as it is, changes over time. Rather than fight this, they used this to their advantage.
As I understand, one of their techniques was to use the visual. The Esso sign was shown in places with the Esso logo up high and prominent. But, down below, was the never-before-seen Exxon sign. It was just there, doing nothing. Doing nothing except implanting itself into the subconscious of the viewers. Then, the Exxon sign, in later ads, appeared higher. The Esso sign lowered and was less prominent. Hmm? What's going on? Does anyone even notice? Hmm? Then, in the coup, the tiger mascot literally lowered the Esso sign down and raised the Exxon sign up.
In the final coup d'état, the Esso sign simply disappeared. And, make no mistake, this is the coup de grâce...the word Esso just disappeared. It was no longer seen at all. Then, it was forgotten and it was gone. Now, there is Exxon.
More recently, we all know that Twitter rebranded to X. It seemed so dumb, definitely awkward, I'm still not entirely used to it, people still write, "...so-and-so posted on X, formerly Twitter,..." (as if no one knows that X is formerly Twitter), I still say people "tweet" on X, but it's changing. I now hear reference to what so-and-so said "on X", with no mention of Twitter. It's changing. Time...it'll change...Twitter will stop being mentioned, Twitter will be a part of history, like Esso.
What'll happen with 21Q?
Nothing. I fully predict that this 2.1 quadrillion bitcoins thing will go nowhere. One of the main reasons for moving to replace "sats" as "bitcoins" is the perception that 1 bitcoin is unattainable and that people know "bitcoin," but don't know "sats." A bull bitcoin is out of reach for most people, but sats are attainable by everyone with a wallet. And, if they don't know ther term "sats," it's probably easier to change that perception (to educate them on sats) than it is to change and possibly confuse their knowledge of 21M bitcoins with 2.1Q bitcoins. It's probably easier to educate on "sats" than it is to change all the backends on exchanges and smart contracts and front ends (and some won't change at all, which will add more to confusion).
Solution: educate
Practical solution: if you think you might be speaking to a "normie" audience, make it a point to use the phrase "bitcoin sats." Over time, as people acquire and use sats to buy burgers, they'll know that sats means 1 of 2.1 quadrillion, but a bitcoin is 1 of 21 million. This is the Esso tiger lowering "bitcoin" and raising "sats."
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ 78b3c1ed:5033eea9
2025-04-27 01:42:48
@ 78b3c1ed:5033eea9
2025-04-27 01:42:48・ThunderHubで焼いたマカロンがlncli printmacaroonでどう見えるか確認した。
ThunderHub macaroon permissions
get invoices invoices:read create invoices invoices:write get payments offchain:read pay invoices offchain:write get chain transactions onchain:read send to chain address onchain:write create chain address address:write get wallet info info:read stop daemon info:write この結果によれば、offchain:wirteとonchain:writeの権限がなければそのマカロンを使うクライアントは勝手にBTCを送金することができない。 info:writeがなければ勝手にLNDを止めたりすることができない。
・lncli printmacaroonでデフォルトで作られるmacaroonのpermissionsを調べてみた。 admin.macaroon
{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "info:read", "info:write", "invoices:read", "invoices:write", "macaroon:generate", "macaroon:read", "macaroon:write", "message:read", "message:write", "offchain:read", "offchain:write", "onchain:read", "onchain:write", "peers:read", "peers:write", "signer:generate", "signer:read" ], "caveats": null }chainnotifier.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "onchain:read" ], "caveats": null }invoice.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "invoices:read", "invoices:write", "onchain:read" ], "caveats": null }invoices.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "invoices:read", "invoices:write" ], "caveats": null }readonly.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "info:read", "invoices:read", "macaroon:read", "message:read", "offchain:read", "onchain:read", "peers:read", "signer:read" ], "caveats": null }router.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "offchain:read", "offchain:write" ], "caveats": null }signer.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "signer:generate", "signer:read" ], "caveats": null }walletkit.macaroon{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "address:read", "address:write", "onchain:read", "onchain:write" ], "caveats": null }・lncli listpermissions コマンドですべての RPC メソッド URI と、それらを呼び出すために必要なマカロン権限を一覧表示できる。 LND v0.18.5-betaでやると1344行ほどのJSONができる。 AddInvoiceだとinvoice:writeのpermissionを持つmacaroonを使えばインボイスを作れるようだ。
"/lnrpc.Lightning/AddInvoice": { "permissions": [ { "entity": "invoices", "action": "write" } ] },lncli listpermissionsからentityとactionを抜き出してみた。 ``` "entity": "address", "entity": "info", "entity": "invoices", "entity": "macaroon", "entity": "message", "entity": "offchain", "entity": "onchain", "entity": "peers", "entity": "signer","action": "generate" "action": "read" "action": "write"
lncli とjqを組み合わせると例えば以下コマンドでinvoices:writeを必要とするRPCの一覧を表示できる。 invoices:writeだとAddInvoiceの他にホドルインボイス作成でも使ってるようだlncli listpermissions | jq -r '.method_permissions | to_entries[] | select(.value.permissions[] | select(.entity == "invoices" and .action == "write")) | .key'/invoicesrpc.Invoices/AddHoldInvoice /invoicesrpc.Invoices/CancelInvoice /invoicesrpc.Invoices/HtlcModifier /invoicesrpc.Invoices/LookupInvoiceV2 /invoicesrpc.Invoices/SettleInvoice /lnrpc.Lightning/AddInvoiceinvoices:readだと以下となる。/invoicesrpc.Invoices/SubscribeSingleInvoice /lnrpc.Lightning/ListInvoices /lnrpc.Lightning/LookupInvoice /lnrpc.Lightning/SubscribeInvoicesLNの主だった機能のRPCはoffchainが必要ぽいので抜き出してみた。 offchain:write チャネルの開閉、ペイメントの送信までやってるみたい。 デフォルトのmacaroonでoffchain:writeを持ってるのはadminとrouterの2つだけ。openchannel,closechannelはonchain:writeのpermissionも必要なようだ。/autopilotrpc.Autopilot/ModifyStatus /autopilotrpc.Autopilot/SetScores /lnrpc.Lightning/AbandonChannel /lnrpc.Lightning/BatchOpenChannel /lnrpc.Lightning/ChannelAcceptor /lnrpc.Lightning/CloseChannel /lnrpc.Lightning/DeleteAllPayments /lnrpc.Lightning/DeletePayment /lnrpc.Lightning/FundingStateStep /lnrpc.Lightning/OpenChannel /lnrpc.Lightning/OpenChannelSync /lnrpc.Lightning/RestoreChannelBackups /lnrpc.Lightning/SendCustomMessage /lnrpc.Lightning/SendPayment /lnrpc.Lightning/SendPaymentSync /lnrpc.Lightning/SendToRoute /lnrpc.Lightning/SendToRouteSync /lnrpc.Lightning/UpdateChannelPolicy /routerrpc.Router/HtlcInterceptor /routerrpc.Router/ResetMissionControl /routerrpc.Router/SendPayment /routerrpc.Router/SendPaymentV2 /routerrpc.Router/SendToRoute /routerrpc.Router/SendToRouteV2 /routerrpc.Router/SetMissionControlConfig /routerrpc.Router/UpdateChanStatus /routerrpc.Router/XAddLocalChanAliases /routerrpc.Router/XDeleteLocalChanAliases /routerrpc.Router/XImportMissionControl /wtclientrpc.WatchtowerClient/AddTower /wtclientrpc.WatchtowerClient/DeactivateTower /wtclientrpc.WatchtowerClient/RemoveTower /wtclientrpc.WatchtowerClient/TerminateSession"/lnrpc.Lightning/OpenChannel": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] },offchain:read readの方はチャネルやインボイスの状態を確認するためのpermissionのようだ。/lnrpc.Lightning/ChannelBalance /lnrpc.Lightning/ClosedChannels /lnrpc.Lightning/DecodePayReq /lnrpc.Lightning/ExportAllChannelBackups /lnrpc.Lightning/ExportChannelBackup /lnrpc.Lightning/FeeReport /lnrpc.Lightning/ForwardingHistory /lnrpc.Lightning/GetDebugInfo /lnrpc.Lightning/ListAliases /lnrpc.Lightning/ListChannels /lnrpc.Lightning/ListPayments /lnrpc.Lightning/LookupHtlcResolution /lnrpc.Lightning/PendingChannels /lnrpc.Lightning/SubscribeChannelBackups /lnrpc.Lightning/SubscribeChannelEvents /lnrpc.Lightning/SubscribeCustomMessages /lnrpc.Lightning/VerifyChanBackup /routerrpc.Router/BuildRoute /routerrpc.Router/EstimateRouteFee /routerrpc.Router/GetMissionControlConfig /routerrpc.Router/QueryMissionControl /routerrpc.Router/QueryProbability /routerrpc.Router/SubscribeHtlcEvents /routerrpc.Router/TrackPayment /routerrpc.Router/TrackPaymentV2 /routerrpc.Router/TrackPayments /wtclientrpc.WatchtowerClient/GetTowerInfo /wtclientrpc.WatchtowerClient/ListTowers /wtclientrpc.WatchtowerClient/Policy /wtclientrpc.WatchtowerClient/Stats・おまけ1 RPCメソッド名にopenを含む要素を抽出するコマンドlncli listpermissions | jq '.method_permissions | to_entries[] | select(.key | test("open"; "i"))'{ "key": "/lnrpc.Lightning/BatchOpenChannel", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } } { "key": "/lnrpc.Lightning/OpenChannel", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } } { "key": "/lnrpc.Lightning/OpenChannelSync", "value": { "permissions": [ { "entity": "onchain", "action": "write" }, { "entity": "offchain", "action": "write" } ] } }・おまけ2 thunderhubで作ったmacaroonはテキストで出力されコピペして使うもので、macaroonファイルになってない。 HEXをmacaroonファイルにするには以下コマンドでできる。HEXをコピペして置換する。またYOURSの箇所を自分でわかりやすい名称に置換すると良い。echo -n "HEX" | xxd -r -p > YOURS.macaroonthunderhubで"Create Invoices, Get Invoices, Get Wallet Info, Get Payments, Pay Invoices"をチェックして作ったmacaroonのpermissionsは以下となる。{ "version": 2, "location": "lnd", "root_key_id": "0", "permissions": [ "info:read", "invoices:read", "invoices:write", "offchain:read", "offchain:write" ], "caveats": null } ``` offchain:writeはあるがonchain:writeがないのでチャネル開閉はできないはず。 -
 @ 58537364:705b4b85
2025-05-18 08:18:45
@ 58537364:705b4b85
2025-05-18 08:18:45Discipline is “doing things with intention, without being swayed or carried away by emotions.” On the other hand, lack of discipline implies the opposite:
Lack of discipline is “acting according to emotional fluctuations or being carried away by feelings,” such as sleepiness, hunger, boredom, frustration, satisfaction, dissatisfaction, fear, infatuation, or lack of mindfulness. This often leads to various excuses like:
- "I'll do it later."
- "I'm too tired."
- "It's too hot or too cold."
- "It's still early."
- "It's already too late."
- Etc.
Building lasting discipline “does not come from force, but from dreams.” The law of dreams states that we must create a clear vision of our ‘heaven’ (goal), then minimize the gap between thought and action. The more we overthink, the less likely we are to act—our mind becomes weak and unstable.
The law of dreams also suggests dreaming for others, not just for oneself. When the mind is overly focused on personal success, wisdom and insight diminish. Actions become self-centered and lack empathy. But when our goal is for the greater good, every action becomes meaningful and contributes to shared happiness and success.
— Metha Harimtepathipbodi
Read the TH full version at: https://w3.do/SODEDpmP
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 7460b7fd:4fc4e74b
2025-05-17 08:26:13
@ 7460b7fd:4fc4e74b
2025-05-17 08:26:13背景:WhatsApp的号码验证与运营商合作关系
作为一款基于手机号码注册的即时通信应用,WhatsApp的账号验证严重依赖全球电信运营商提供的短信或电话服务。这意味着,当用户注册或在新设备登录WhatsApp时,WhatsApp通常会向用户的手机号码发送SMS短信验证码或发起语音电话验证。这一流程利用了传统电信网络的基础设施,例如通过SS7(信令系统7)协议在全球范围内路由短信和电话securityaffairs.com。换句话说,WhatsApp把初始账户验证的安全性建立在电信运营商网络之上。然而,这种依赖关系也带来了隐患:攻击者可以利用电信网络的漏洞来拦截验证码。例如,研究人员早在2016年就演示过利用SS7协议漏洞拦截WhatsApp和Telegram的验证短信,从而劫持用户账户的攻击方法securityaffairs.com。由于SS7协议在全球范围内连接各国运营商,一个运营商的安全缺陷或恶意行为都可能被不法分子利用来获取他网用户的短信验证码securityaffairs.com。正因如此,有安全专家指出,仅依赖短信验证不足以保障账户安全,WhatsApp等服务提供商需要考虑引入额外机制来核实用户身份securityaffairs.com。
除了技术漏洞,基于电信运营商的验证还受到各地政策和网络环境影响。WhatsApp必须与全球各地运营商“合作”,才能将验证码送达到用户手机。然而这种“合作”在某些国家可能并不顺畅,典型例子就是中国。在中国大陆,国际短信和跨境电话常受到严格管控,WhatsApp在发送验证码时可能遭遇拦截或延迟sohu.com。因此,理解WhatsApp在中国的特殊联网和验证要求,需要将其全球验证机制与中国的电信政策和网络审查环境联系起来。下文将深入探讨为什么在中国使用WhatsApp进行号码验证时,必须开启蜂窝移动数据,并分析其中的技术逻辑和政策因素。
中国环境下的特殊问题:为何必须开启蜂窝数据?
中国的网络审查与封锁: WhatsApp自2017年起就在中国大陆遭遇严格封锁。起初,WhatsApp在华的服务受到**“GFW”(防火长城)**的部分干扰——例如曾一度只能发送文本消息,语音、视频和图片消息被封锁theguardian.com。到2017年下半年,封锁升级,很多用户报告在中国完全无法使用WhatsApp收发任何消息theguardian.com。中国官方将WhatsApp与Facebook、Telegram等西方通信平台一同屏蔽,视作对国家网络主权的挑战theguardian.com。鉴于此,在中国境内直接访问WhatsApp的服务器(无论通过Wi-Fi还是本地互联网)都会被防火长城所阻断。即使用户收到了短信验证码,WhatsApp客户端也无法在没有特殊连接手段的情况下与服务器完成验证通信。因此,单纯依赖Wi-Fi等本地网络环境往往无法完成WhatsApp的注册或登陆。很多用户经验表明,在中国使用WhatsApp时需要借助VPN等工具绕过审查,同时尽可能避免走被审查的网络路径sohu.com。
强制Wi-Fi热点与连接策略: 除了国家级的封锁,用户所连接的局域网络也可能影响WhatsApp验证。许多公共Wi-Fi(如机场、商场)采取强制门户认证(captive portal),用户需登录认证后才能上网。对此,WhatsApp在客户端内置了检测机制,当发现设备连入这类强制Wi-Fi热点而无法访问互联网时,会提示用户忽略该Wi-Fi并改用移动数据faq.whatsapp.com。WhatsApp要求对此授予读取Wi-Fi状态的权限,以便在检测到被拦截时自动切换网络faq.whatsapp.com。对于中国用户来说,即便所连Wi-Fi本身联网正常,由于GFW的存在WhatsApp依然可能视之为“不通畅”的网络环境。这也是WhatsApp官方指南中强调:如果Wi-Fi网络无法连接WhatsApp服务,应直接切换到手机的移动数据网络faq.whatsapp.com。在中国,由于本地宽带网络对WhatsApp的封锁,蜂窝数据反而成为相对可靠的通道——尤其在搭配VPN时,可以避开本地ISP的审查策略,实现与WhatsApp服务器的通信sohu.com。
国际短信的运营商限制: 使用移动数据还有助于解决短信验证码接收难题。中国的手机运营商出于防垃圾短信和安全考虑,默认对国际短信和境外来电进行一定限制。许多中国用户发现,注册WhatsApp时迟迟收不到验证码短信,原因可能在于运营商将来自国外服务号码的短信拦截或过滤sohu.com。例如,中国移动默认关闭国际短信接收,需要用户主动发送短信指令申请开通sohu.com。具体而言,中国移动用户需发送文本“11111”到10086(或10085)来开通国际短信收发权限;中国联通和电信用户也被建议联系运营商确认未屏蔽国际短信sohu.com。若未进行这些设置,WhatsApp发送的验证码短信可能根本无法抵达用户手机。在这种情况下,WhatsApp提供的备用方案是语音电话验证,即通过国际电话拨打用户号码并播报验证码。然而境外来电在中国也可能遭到运营商的安全拦截,特别是当号码被认为可疑时zhuanlan.zhihu.com。因此,中国用户经常被建议开启手机的蜂窝数据和漫游功能,以提高验证码接收的成功率sohu.com。一方面,开启数据漫游意味着用户准备接受来自境外的通信(通常也包含短信/电话);另一方面,在数据联网的状态下,WhatsApp可以尝试通过网络直接完成验证通信,从而减少对SMS的依赖。
移动数据的网络路径优势: 在实际案例中,一些中国WhatsApp用户报告仅在开启蜂窝数据的情况下才能完成验证。这可能归因于蜂窝网络和宽带网络在国际出口上的差异。中国移动、联通等运营商的移动数据可能走与宽带不同的网关路由,有时对跨境小流量的拦截相对宽松。此外,WhatsApp在移动数据环境中可以利用一些底层网络特性。例如,WhatsApp可能通过移动网络发起某些专用请求或利用运营商提供的号码归属地信息进行辅助验证(虽然具体实现未公开,但这是业界讨论的可能性)。总之,在中国特殊的网络环境下,开启蜂窝数据是确保WhatsApp验证流程顺利的重要一步。这一步不仅是为了基本的互联网连接,也是为了绕开种种对国际短信和应用数据的拦截限制,从而与WhatsApp的全球基础设施建立必要的通讯。
PDP Context与IMSI:移动网络验证的技术细节
要理解为什么移动数据对WhatsApp验证如此关键,有必要了解移动通信网络中的一些技术细节,包括PDP Context和IMSI的概念。
PDP Context(分组数据协议上下文): 当手机通过蜂窝网络使用数据(如4G/5G上网)时,必须先在运营商核心网中建立一个PDP上下文。这实际上就是申请开启一个数据会话,运营商将为设备分配一个IP地址,并允许其通过移动核心网访问互联网datascientest.com。PDP上下文包含了一系列参数(例如APN接入点名称、QoS等级等),描述该数据会话的属性datascientest.comdatascientest.com。简单来说,激活蜂窝数据就意味着创建了PDP上下文,设备获得了移动网络网关分配的IP地址,可以收发数据包。对于WhatsApp验证而言,只有在建立数据连接后,手机才能直接与WhatsApp的服务器交换数据,例如提交验证码、完成加密密钥协商等。如果仅有Wi-Fi而蜂窝数据关闭,且Wi-Fi环境无法连通WhatsApp服务器,那么验证过程将陷入停滞。因此,在中国场景下,开启蜂窝数据(即建立PDP数据通路)是WhatsApp客户端尝试绕过Wi-Fi限制、直接通过移动网络进行验证通信的前提faq.whatsapp.comsohu.com。值得一提的是,PDP Context的建立也表明手机在运营商网络上处于活跃状态,这对于某些验证机制(比如后述的闪信/闪呼)来说至关重要。
IMSI与MSISDN: IMSI(国际移动用户标识)和MSISDN(移动用户号码,即手机号码)是运营商网络中两个密切相关但不同的标识。IMSI是存储在SIM卡上的一串唯一数字,用于在移动网络中标识用户身份netmanias.com。当手机接入网络时,它向运营商提供IMSI以进行鉴权,运营商据此知道“是哪张SIM”的请求netmanias.com。而MSISDN则是我们平常说的手机号,用于在语音通话和短信路由中定位用户,也存储在运营商的HLR/HSS数据库中netmanias.com。运营商通过IMSI<->MSISDN的对应关系,将来自全球的短信/电话正确路由到用户手机上。WhatsApp的验证短信或电话本质上就是通过目标号码(MSISDN)寻找所属运营商网络,由该网络根据IMSI定位用户终端。一般情况下,WhatsApp应用并不直接接触IMSI这种信息,因为IMSI属于运营商网络的内部标识。然而,IMSI的存在仍然对安全产生影响。例如,**SIM卡交换(SIM Swap)**欺诈发生时,攻击者获得了受害者号码的新SIM卡,新SIM卡会有不同的IMSI,但MSISDN保持原号码不变。运营商会将原号码映射到新的IMSI,这样验证码短信就发送到了攻击者手中的SIM上。对WhatsApp而言,除非有机制检测IMSI变动,否则无法察觉用户号码背后的SIM已被盗换。部分应用在检测到SIM变化时会提示用户重新验证,这需要读取设备的IMSI信息进行比对。然而,在现代智能手机中,获取IMSI通常需要特殊权限,WhatsApp并未明确说明它有此类检测。因此,从WhatsApp角度,IMSI更多是网络侧的概念,但它提醒我们:电信级身份验证依赖于SIM的有效性。只有当正确的IMSI在网络注册、并建立了PDP数据上下文时,WhatsApp的后台服务才能确认该SIM对应的号码目前“在线”,进而可靠地发送验证信号(短信或电话)到该设备。
移动网络的信号辅助验证: 有观点认为,一些OTT应用可能利用移动网络提供的附加服务来辅助号码验证。例如,某些运营商提供号码快速验证API,当应用检测到设备在移动数据网络中时,可以向特定地址发起请求,由运营商返回当前设备的号码信息(通常通过已经建立的PDP通道)。Google等公司在部分国家与运营商合作过类似服务,实现用户免输入验证码自动完成验证。但就WhatsApp而言,没有公开证据表明其使用了运营商提供的自动号码识别API。即便如此,WhatsApp鼓励用户保持移动网络在线的做法,隐含的意义之一可能是:当手机处于蜂窝网络且数据畅通时,验证码通过率和验证成功率都会显著提升。这既包括了物理层面短信、电话能否送达,也涵盖了数据层面应用和服务器能否互通。
Flash Call机制:WhatsApp验证的新方案
针对传统SMS验证码容易被拦截、延迟以及用户体验不佳的问题,WhatsApp近年来引入了一种Flash Call(闪呼)验证机制fossbytes.com。所谓闪呼,即应用在用户验证阶段向用户的手机号发起一个非常短暂的来电:用户无需真正接听,WhatsApp会自动结束这通电话,并根据通话记录来确认是否拨通fossbytes.com。
原理与流程: 当用户选择使用闪呼验证(目前主要在Android设备上可用),WhatsApp会请求权限访问用户的通话记录fossbytes.com。随后应用拨打用户的号码,一般是一个预先设定的特定号码或号码段。由于WhatsApp后台知道它拨出的号码及通话ID,只要该未接来电出现在用户手机的通话日志中,应用即可读取并匹配最后一通来电的号码是否符合验证要求,从而确认用户持有这个号码fossbytes.com。整个过程用户无需手动输入验证码,验证通话在数秒内完成。相比6位数字短信验证码需要用户在短信和应用间切换输入,闪呼方式更加快捷无缝fossbytes.com。
优缺点分析: 闪呼验证的优势在于速度快且避免了SMS可能的延迟或拦截。一些分析指出闪呼将成为取代SMS OTP(一次性密码)的新趋势,Juniper Research预测2022年用于验证的闪呼次数将从2021年的六千万猛增到五十亿次subex.comglobaltelcoconsult.com。对于WhatsApp这样全球用户庞大的应用,闪呼可以节约大量SMS网关费用,并绕开部分运营商对国际SMS的限制。然而,闪呼也有局限:fossbytes.com首先,iOS设备由于系统安全限制,应用无法访问通话记录,因此iPhone上无法使用闪呼验证fossbytes.com。这意味着苹果用户仍需使用传统短信验证码。其次,为实现自动匹配来电号码,用户必须授予读取通话记录的权限,这在隐私上引发一些担忧fossbytes.comfossbytes.com。WhatsApp声称不会将通话记录用于验证以外的用途,号码匹配也在本地完成fossbytes.com,但考虑到母公司Meta的隐私争议,部分用户依然顾虑。第三,闪呼验证依赖语音通话路线,同样受制于电信网络质量。如果用户所处网络无法接通国际来电(比如被运营商拦截境外短振铃电话),闪呼也无法成功。此外,从运营商角度看,闪呼绕过了A2P短信计费,可能侵蚀短信营收,一些运营商开始研究识别闪呼流量的策略wholesale.orange.com。总体而言,闪呼机制体现了WhatsApp希望减轻对短信依赖的努力,它在许多国家提升了验证体验,但在中国等特殊环境,其效果仍取决于本地语音网络的开放程度。值得注意的是,中国运营商对于境外电话,尤其是这种**“零响铃”未接来电**也有防范措施,中国电信和联通用户就被建议如需接收海外来电验证,应联系客服确保未拦截海外来电hqsmartcloud.com。因此,即便WhatsApp支持闪呼,中国用户若未开启移动语音漫游或运营商许可,仍然难以通过此途径完成验证。
与SIM Swap安全性的关系: 从安全角度看,闪呼并未实质提升抵御SIM交换攻击的能力。如果攻击者成功将受害者的号码转移至自己的SIM卡上(获取新IMSI),那么无论验证码以短信还是闪呼方式发送,都会到达攻击者设备。闪呼机制能防御的是部分恶意拦截短信的行为(如恶意网关或木马读取短信),但对社工换卡没有太大帮助。WhatsApp早已提供两步验证(即设置6位PIN码)供用户自行启用,以防号码被他人重新注册时需要额外密码。然而大量用户未开启该功能。因此,闪呼更多是从用户体验和成本出发的改良,而非针对高级别攻击的防护机制。正如前文所述,真正要防御SIM Swap和SS7漏洞等系统性风险,依赖运营商的号码验证本身就是薄弱环节,需要引入更高级的身份认证手段。
SIM卡交换攻击的风险与运营商信任问题
WhatsApp和Telegram一类基于手机号认证的应用普遍面临一个安全挑战:手机号码本身并非绝对安全的身份凭证。攻击者可以通过一系列手段取得用户的号码控制权,其中SIM交换(SIM Swap)是近年高发的欺诈手法。SIM Swap通常由不法分子冒充用户,诱骗或贿赂运营商客服将目标号码的服务转移到攻击者的新SIM卡上keepnetlabs.com。一旦成功,所有发往该号码的短信和电话都转由攻击者接收,原机主的SIM卡失效。对于依赖短信/电话验证的应用来说,这意味着攻击者可以轻易获取验证码,从而重置账户并登录。近年来全球SIM Swap案件呈上升趋势,许多在线服务的账号被此攻破rte.ie。
WhatsApp并非未知晓此风险。事实上,WhatsApp在其帮助中心和安全博客中多次提醒用户开启两步验证PIN,并强调绝不向他人透露短信验证码。然而,从系统设计上讲,WhatsApp仍将信任根基放在运营商发送到用户手机的那串数字验证码上。一旦运营商端的安全被绕过(无论是内部员工作恶、社工欺诈,还是SS7网络被黑客利用securityaffairs.com),WhatsApp本身无法辨别验证码接收者是否是真正的用户。正如安全研究所Positive Technologies指出的那样,目前主要的即时通讯服务(包括WhatsApp和Telegram)依赖SMS作为主要验证机制,这使得黑客能够通过攻击电信信令网络来接管用户账户securityaffairs.com。换言之,WhatsApp被迫信任每一个参与短信/电话路由的运营商,但这个信任链条上任何薄弱环节都可能遭到利用securityaffairs.com。例如,在SIM Swap攻击中,运营商本身成为被欺骗的对象;而在SS7定位拦截攻击中,全球互联的电信网成为攻击面。在中国的场景下,虽然主要威胁来自审查而非黑客,但本质上仍是WhatsApp无法完全掌控电信网络这一事实所导致的问题。
应对这些风险,WhatsApp和Telegram等采用了一些弥补措施。除了提供用户自行设定的二次密码,两者也开始探索设备多因子的概念(如后文Telegram部分所述,利用已有登录设备确认新登录)。然而,对绝大多数首次注册或更换设备的用户来说,传统的短信/电话验证仍是唯一途径。这就是为什么在高安全需求的行业中,SMS OTP正逐渐被视为不充分securityaffairs.com。监管机构和安全专家建议对涉敏感操作采用更强验证,如专用身份应用、硬件令牌或生物识别等。WhatsApp作为大众通信工具,目前平衡了易用性与安全性,但其依赖电信运营商的验证模式在像中国这样特殊的环境下,既遇到政策阻碍,也隐藏安全短板。这一点对于决策制定者评估国外通信应用在华风险时,是一个重要考量:任何全球运营商合作机制,在中国境内都可能因为**“最后一公里”由中国运营商执行**而受到影响。无论是被拦截信息还是可能的监控窃听,这些风险都源自于底层通信网的控制权不在应用服务商手中。
Telegram登录机制的比较
作为对比,Telegram的账号登录机制与WhatsApp类似,也以手机号码为主要身份标识,但在具体实现上有一些不同之处。
多设备登录与云端代码: Telegram从设计上支持多设备同时在线(手机、平板、PC等),并将聊天内容储存在云端。这带来的一个直接好处是:当用户在新设备上登录时,Telegram会优先通过已登录的其他设备发送登录验证码。例如,用户尝试在电脑上登录Telegram,Telegram会在用户手机上的Telegram应用里推送一条消息包含登录码,而不是立即发短信accountboy.comaccountboy.com。用户只需在新设备输入从老设备上收到的代码即可完成登录。这种机制确保了只要用户至少有一个设备在线,就几乎不需要依赖运营商短信。当然,如果用户当前只有一部新设备(例如换了手机且旧设备不上线),Telegram才会退而求其次,通过SMS发送验证码到手机号。同时,Telegram也允许用户选择语音电话获取验证码,类似于WhatsApp的语音验证。当用户完全无法收到SMS时(比如在中国这种场景),语音呼叫常常比短信更可靠seatuo.com。
两步验证密码: 与WhatsApp一样,Telegram提供可选的两步验证密码。当启用此功能后,即使拿到短信验证码,仍需输入用户设置的密码才能登录账户quora.com。这对抗SIM Swap等攻击提供了另一层防线。不过需要指出,如果用户忘记了设置的Telegram密码且没有设置信任邮箱,可能会永久失去账号访问,因此开启该功能在中国用户中接受度一般。
登录体验与安全性的取舍: Telegram的登录流程在用户体验上更加灵活。多设备下无需每次都收验证码,提高了便利性。但从安全角度看,这种“信任已有设备”的做法也有隐患:如果用户的某个设备落入他人之手并未及时登出,那么该人有可能利用该设备获取新的登录验证码。因此Telegram会在应用中提供管理活动会话的功能,用户可随时查看和撤销其它设备的登录状态telegram.org。总体而言,Telegram和WhatsApp在初始注册环节同样依赖短信/电话,在这一点上,中国的网络环境对两者影响相似:Telegram在中国同样被全面封锁,需要VPN才能使用,其短信验证码发送也会受到运营商限制。另外,Telegram曾在2015年因恐怖分子利用该平台传递信息而被中国当局重点关注并屏蔽,因此其国内可达性甚至比WhatsApp更低。许多中国用户实际使用Telegram时,通常绑定国外号码或通过海外SIM卡来收取验证码,以绕开国内运营商的限制。
差异总结: 简而言之,Telegram在登录验证机制上的主要优势在于已有会话协助和云端同步。这使得老用户换设备时不依赖国内短信通道即可登录(前提是原设备已登录并可访问)。WhatsApp直到最近才推出多设备功能,但其多设备模式采用的是端到端加密设备链路,需要主手机扫码授权,而非像Telegram那样用账号密码登录其它设备。因此WhatsApp仍然强绑定SIM卡设备,首次注册和更换手机号时逃不开运营商环节。安全方面,两者的SMS验证所面临的系统性风险(如SS7攻击、SIM Swap)并无本质区别,都必须仰仗运营商加强对核心网络的保护,以及用户自身启用附加验证措施securityaffairs.comkeepnetlabs.com。
结论
对于希望在中国使用WhatsApp的用户来说,“开启蜂窝数据”这一要求背后体现的是技术与政策交织的复杂现实。一方面,蜂窝数据承载着WhatsApp与其全球服务器通信的关键信道,在中国的受限网络中提供了相对可靠的出路faq.whatsapp.comsohu.com。另一方面,WhatsApp的号码验证机制深深植根于传统电信体系,必须经由全球运营商的“协作”才能完成用户身份确认securityaffairs.com。而在中国,这种协作受到防火长城和运营商政策的双重阻碍:国际短信被拦截、国际数据被阻断。为克服这些障碍,WhatsApp既采取了工程上的应对(如检测强制Wi-Fi并提示使用移动网络faq.whatsapp.com),也引入了诸如闪呼验证等新方案以减少对短信的依赖fossbytes.com。但从根本上说,只要注册流程离不开手机号码,这种与电信运营商的捆绑关系就无法割舍。由此带来的安全问题(如SIM Swap和信令网络漏洞)在全球范围内敲响警钟securityaffairs.comkeepnetlabs.com。
对于从事安全研究和政策评估的人士,这篇分析揭示了WhatsApp在中国遇到的典型困境:技术系统的全球化与监管环境的本地化冲突。WhatsApp全球统一的验证框架在中国水土不服,不得不通过额外的设置和手段来“曲线救国”。这既包括让用户切换网络、配置VPN等绕过审查,也包括思考未来是否有必要采用更安全独立的验证方式。相比之下,Telegram的机制给出了一种启示:灵活运用多设备和云服务,至少在一定程度上降低对单一短信渠道的依赖。然而,Telegram自身在中国的处境表明,再优雅的技术方案也难以直接对抗高强度的网络封锁。最终,无论是WhatsApp还是Telegram,要想在受限环境下可靠运作,都需要技术与政策的双管齐下:一方面提高验证与登录的安全性和多样性,另一方面寻求运营商和监管层面的理解与配合。
综上所述,WhatsApp要求中国用户开启蜂窝数据并非偶然的臆想,而是其全球运营商合作验证机制在中国受阻后的务实选择。这一要求折射出移动通信应用在跨境运营中面临的挑战,也提醒我们在设计安全策略时必须考虑底层依赖的信任假设。对于个人用户,最实际的建议是在使用此类应用时提前了解并遵循这些特殊设置(如开通国际短信、启用数据漫游),并善用应用自身的安全功能(如两步验证)来保护账户免遭社工和网络攻击keepnetlabs.com。对于监管和运营商,则有必要权衡安全审查与用户便利之间的平衡,在可控范围内为可信的全球服务留出技术通道。在全球通信愈加融合的时代,WhatsApp的中国验证问题或许只是一个缩影,背后涉及的既有网络安全考量,也有数字主权与国际合作的议题,值得持续深入研究和关注。
faq.whatsapp.comfossbytes.comtheguardian.comsecurityaffairs.comsecurityaffairs.comkeepnetlabs.comdatascientest.comnetmanias.comsohu.comsohu.com
-
 @ 58537364:705b4b85
2025-05-18 08:18:23
@ 58537364:705b4b85
2025-05-18 08:18:23The Dhamma of the Buddha is not merely a concept or philosophical hypothesis. It is the direct seeing of the truth — that suffering truly exists within us, and that it can genuinely be ended — through observing, with wisdom, not by calculation or blind belief.
Suffering is not an abstract idea; it is a real experience we can feel. When we truly understand suffering by facing it directly — not running from it or deceiving ourselves — we will see that the sense of “self” is the root of suffering. Every time the feeling of “this is me, this is mine” arises — suffering follows.
The solution is not in argument or debate, but in taking action to see and know this truth for ourselves.
Thus, Dhamma is the science of the mind — not just a philosophy. And this is why the Buddha’s teachings have never become outdated, even after more than 2,500 years.
Read the TH full version at: https://w3.do/okHFEDy-
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ c9badfea:610f861a
2025-05-17 03:08:55
@ c9badfea:610f861a
2025-05-17 03:08:55- Install Rethink (it's free and open source)
- Launch the app and tap Skip
- Tap Start and then Proceed to set up the VPN connection
- Allow notifications and Proceed, then disable battery optimization for this app (you may need to set it to Unrestricted)
- Navigate to Configure and tap Apps
- On the top bar, tap 🛜 and 📶 to block all apps from connecting to the internet
- Search Apps for the apps you want to allow and Bypass Universal
- Return to the Configure view and tap DNS, then choose your preferred DNS provider (e.g. DNSCrypt > Quad9)
- Optionally, tap On-Device Blocklists, then Disabled, Download Blocklists, and later Configure (you may need to enable the Use In-App Downloader option if the download is not working)
- Return to the Configure view and tap Firewall, then Universal Firewall Rules and enable the options as desired:
- Block all apps when device is locked
- Block newly installed apps by default
- Block when DNS is bypassed
- Optionally, to set up WireGuard or Tor, return to the Configure view and tap Proxy
- For Tor, tap Setup Orbot, then optionally select all the apps that should route through Tor (you must have Orbot installed)
- For WireGuard, tap Setup WireGuard, then +, and select an option to import a WireGuard configuration (QR Code Scan, File Import, or Creation).
- Use Simple Mode for a single WireGuard connection (all apps are routed through it).
- Use Advanced Mode for multiple WireGuard connections (split tunnel, manually choosing apps to route through them)
⚠️ Use this app only if you know what you are doing, as misconfiguration can lead to missing notifications and other problems
ℹ️ On the main view, tap Logs to track all connections
ℹ️ You can also use a WireGuard connection (e.g., from your VPN provider) and on-device blocklists together
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ c9badfea:610f861a
2025-05-14 18:38:04
@ c9badfea:610f861a
2025-05-14 18:38:04- Install KeePassDX (it's free and open source)
- Launch the app, tap Create New Vault, and choose a location to store the database file
- Activate the Password slider
- Type a Password and Confirm Password, then tap OK
- Tap + and Add Entry to add your first credentials
- Enter a Title, Username, and Password (you can also generate a password here)
- Tap ✓ at the bottom to create the entry
- Tap ⋮ and then Save Data to save the database
- Tap 🔒 to lock the database
⚠️ Make sure you use strong, high-entropy passphrases
⚠️ Back up the database file to a secure location (e.g. encrypted USB drive)
ℹ️ The database file (
.kdbx) can also be opened with various KeePass ports -
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 83279ad2:bd49240d
2025-05-18 07:27:02
@ 83279ad2:bd49240d
2025-05-18 07:27:02nostr:nevent1qvzqqqr4gupzpqe8ntfgamz8sh3p88w99x5k2r7mksjrvm2xghju9qj00j75jfqdqythwumn8ghj7un9d3shjtnswf5k6ctv9ehx2ap0qy88wumn8ghj7mn0wvhxcmmv9uq3wamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmny9uq3wamnwvaz7tmjv4kxz7fwwpexjmtpdshxuet59uq3wamnwvaz7tmnv4shycmg9ehx7ueww3hkgcte9uq3wamnwvaz7tmnv4shycmg9ehx7ueww3hkgcte9uq3wamnwvaz7tmjv4kxz7fwwpexjmtpdshxuet59uqsuamnwvaz7tmwdaejumr0dshsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshsz9mhwden5te0wfjkccte9ec8y6tdv9kzumn9wshszrnhwden5te0dehhxtnvdakz7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgwwaehxw309ahx7uewd3hkctcqyznaykvq5f87swdlg0tf4u8zph2k0snnwnjwdsm59uun96nuya70wzx2z50
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 5df413d4:2add4f5b
2025-05-13 12:37:20
@ 5df413d4:2add4f5b
2025-05-13 12:37:20https://i.nostr.build/Ur1Je684aSgYCRn3.jpg
You Are Not A Gadget by Jaron Lanier
Reading Jaron Lanier’s 2010 You Are Not A Gadget in 2023 is an interesting experience—equal parts withering, prophetic, and heretical clarion call warning from a high priest of the Technocracy and rambling, musing, cognitive jam session from a technofied musician-philosopher.
Yet, in ways that I think the author would be simultaneously pleased, amused, saddened, and disturbed by, the 13 yeas since the book’s publishing have, in places, proven him right with stunning foresight and precision, and in others, made his ideas appear laughable, bizarre, even naive. The book is written in five parts, yet I would suggest viewing it as two discrete elements—Part One (around the first half of the book) and…everything else.
For context, Lanier, is a computer scientist and early technologist from the area of Jobs, Wozniak, and Gates, and is considered to be a founding father of virtual reality. He is also a consummate contrarian, a player of rare and obscure musical instruments, a deep interdisciplinary thinker…and a white man with dreadlocks named Jaron.
PART ONE
Part One of the book “What is a Person?” reads like a scathing and clear-eye manifesto—where Lanier is batting 1000, merciless in his rightness. Were one to pull a passage that speaks to the soul of this portion of the book, it might be the following: “The net does not design itself. We design it.”
Lanier terms the prevailing technocratic ideology—the particular winning tech-nerd subculture that has now come to capture our society—as “the cybernetic totalist” or “digital Maoists.” Essentially a materialist and stealth collectivist movement in new-age technocratic dress, that through its successes, and now excesses, represents much the same of religion that it’s founders would have claimed to be “evolving past.”
Lanier points out that in this, we are simply trading the pursuit of finding God in spirituality or the afterlife, for a notion of digital immortality—seeking, or, if possible, becoming, God in the cloud. He aptly identifies that this worldview requires that society, and all human interactions really, be savagely bent into adherence to this new religion of aggregation that demands deification of data, gross diminishment of the individual, and belief in some objective (but never defined) "meaning" that exists beyond and apart from the human observer.
With skill and simple wit, he raises strong, rational counterpoint to the digital Maoists’ obsession with quantity, data in aggregate and at-scale, as society's prime directive “A fashionable idea in technical circles is that quantity […] turns into quality at some extreme scale […] I disagree. A trope in the early days or computer science comes to mind: garbage in, garbage out.”
Lanier is able to envision the digital cages that likes of Facebook, Youtube, social-media dating apps would become for the internet native generations. Of whom he writes “The most effective young Facebook users […] are the ones who create successful online fictions about themselves,” and “If you start out by being fake, you’ll eventually have to put in twice the effort to undo the illusion if anything good is to come of it.”
Lanier’s 2010 criticism of Wikipedia-ism is now double or triply apropos in our current hype cycle of “AI magic” and Everything-GPT, “Wikipedia, for instance, works on what I can the Oracle Illusion, in which knowledge of human authorship of a text is suppressed in order to give the text superhuman validity. Traditional holy books work in precisely the same way and present many of the same problems.” This same deep truth now sits at the heart of every “new” creation churned out by the flavor-of-the-week, plagiarism-at-scale, generative AI tool.
More darkly, he is also able to foresee the spectre of a return to collectivism lurking both at the core and on the margins of our new digital age—“The recipe that led to social catastrophe in the past was economic humiliation combined with collectivist ideology. We already have the ideology in its new digital packaging, and it’s entirely possible we could face dangerously traumatic economic shock in the coming decades.”—“No Shit” said everyone who lived through 2020-2022…
This brings us, eerily, to the world of today. Where aggregate insights are upheld as more valuable than discrete insights. Where crowds are are assumed to have more wisdom than individuals. Where truth is twisted into a might-is-right numbers game. A world ruled by the idea that if we can just centralize enough information and sufficiently pulverize authorship, the result will, necessarily, be something super-intelligent, "alive," and perhaps even divine.
In short, the cybernetic totalists and digital Maoists, having killed reason, now sit on its corpse like a thrown, smearing its blood on the walls in the name of art and reading its still-steaming entrails for prophecy.
If I were to infer some ideological takeaway from Part One of the book, it might be that Lanier seems to axiomatically reject any affirmative implication of the Turing Test. Simply put, he believes that bits are not and cannot ever be alive independent of the human-as-oracle. Further, there is no objective meaning beyond the human observer—in fact, that observer fundamentally creates any meaning there is to be had. This is best illustrated by one of the most powerful passages in the book:
“But the Turing Test cuts both ways. You can’t tell if a machine has gotten smarter or if you’ve just lowered your own standard of intelligence to such a degree that the machine seems smart. If you can have a conversation with a simulated person presented by an AI program, can you tell how far you’ve let your sense of personhood degrade in order to make the illusion work for you?”
Ponder this well, Anon.
EVERYTHING ELSE
With all of the great stuff above out of the way, we must turn to…the rest of the book. Parts Two through Five breakdown into something more like a stream of consciousness. And while there are certainly many nuggets to insight and beauty to be found, the book becomes largely dis-coherent and very difficult to read. That said, the remainder of the book does contain three particularly compelling threads that I find to be worth pulling on.
Internet Attribution First, are Lanier’s musing about money and attribution in our authorless “information wants to be free” world. He laments the infinite elevation of advertising and offers harsh critique to the concept of attention as the new currency—as this tends to overwhelmingly reward the aggregator and a piddling few soulless super-influencers at the expense of all other users and creators.
Interestingly, under the guise of “what could have been” he imagines a world where attribution is tracked across the web (though how this achieved is left unanswered) and royalty payments can flow back to the author seamlessly over the internet. I find his vision to be intriguing because in 2010, we lacked the technology to either track attribution across the web or facilitate seamless micropayment royalties based on access / usage.
While we still don't have the ability to achieve the type of fully-tracked, always-on attribution Lanier imagines, we do now have the ability to stream payments across the internet with bitcoin and the lightning network. While Lanier can be excused for not mentioning the then uber-nascent bitcoin in 2010, bitcoin’s development since only goes to underscore the prescience of Lanier’s imagination.
The bigger question that now remains, especially in the face of the advent of “AI,” is whether such a system to manage and therefore enforce attribution globally on the internet would even be a good thing. Where obscured attribution enables mashed-up plagiarism-at-scale, centrally enforced attribution can just as easily enable idea, content, discovery, and innovation suppression-at-scale.
Music in the New Age Second, much of the book, particularly in the second half, is filtered through the lens and language of music. Music is essential to Lanier’s inner life and it is clear that he views music as an emergent mystery force attributable to something unknowable, if not divine, and entirely unique to the human experience.
He bemoans the music of the 2000s as lacking in any distinct chronological era sound—everything is either a rehashed mashup or digitally lofi-ed emulation of sounds from previous begone eras—it is music that is impossible to place. To him, it is as though musical evolution stopped right around the time of the advent of the internet…and then folded back in on itself, creating an endless kaleidoscoping of what came before but rarely, if ever, the creation anything truly new.
In response, Lanier goes so far as to imagine the ridiculous (my take, not his) world of “Songles”—songs on dongles—essentially physical music NFTs. In Songleland, listening to the hottest tracks at a party hinges on the guy or gal with the dankest songles swinging through and plugging them into the Songle player. And songles, being scarce, even become speculative investments. On this, Lanier manages to be both right and wrong in only the most spectacularly absurd of ways.
But what Lanier really laments is the passing of popular music as a shared cultural experience at national or even global scale. During Lanier’s coming of age through the 1960-80s—with only a few consolidated channels for music distribution, it was truly impossible to escape the sounds and influence of the Beatles or Prince or Micheal Jackson—everyone heard it and even the deaf still felt it.
In the end, Lanier could image Songles but he couldn’t envision what Spotify would become—a conduit to shatter music distribution into a myriad of tiny longtails—providing infinitely fragmented and individually fine-tuned music experiences rather than large and cohesive cultural moments. However, even in this miss, Lanier is largely able to project what Spotify-ed music would resolve to—music designed as much or more to please the self-referential selection algorithm than any real, human listeners. A dangerously foretelling insight that goes well beyond music as AI tools are posed to become the "googling" of the next technological cycle—what happens to information, to human thought, when the majority of "generative AI" outputs are just the machine referencing itself?
Digital Neoteny The final thread to pull is that of "digital neoteny," the retention of juvenile behaviors in adult form, in this case, a neoteny of the mind if you will. Lanier sees the internet as specifically primed to propagate three kinds of neoteny in digital-native humans— a blissful and curious Bachelardian neoteny (as in Gaston Bachelard’s Poetics of Reverie); a cruel and mob-like Goldingesque neoteny (as in William Golding’s Lord of the Flies); and a general and deeply pervasive, infantile neoteny.
Neoteny of the Bachelardian variety, which Lanier likens to “the sense of wonder and weirdness that a teen can find in the unfolding world,” is what he feels the internet has provided in a few brief and magical moments generally aligned with the “early days” of successive internet technologies, movements, and companies—through this generally degrades into Goldingesque neoteny as novelty gives way to ossification.
Lanier’s missives on Bachelardian neoteny feel especially pertinent to the present state of Nostr (where I am publishing this writing). Nostr is in a moment where winner-take all dynamics and corporatization have yet to take hold. Child-like revelry abounds with each new discovery or novel Nostr client development so much so that the likes of Jack Dorsey compare it to the excitement of the early internet.
But with time, if and as the Nostr protocol wins, to what extent will technical lock-in take hold here? To what extent will calcification of seemingly trivial or even comical decisions being made by client devs today have dramatic implications on the feasibility of other development in the future? And will we early Nostr users, at some point put down welcoming inclusivesness for insular tribalism—and in what ways might we be doing this already?
Finally, to the third kind of neoteny, Infantile neoteny—which perhaps incapsulates the internet even more so than either of the other two types—Lanier sees the net driving an evermore prolonged deferral of maturity, resulting ultimately in some centrally-managed permanent arresting of society in a stupefied and juvenile mental state:
“Some of the greatest speculative investments in human history continue to converge on Silicon Valley schemes that seemed to have been named by Dr. Seuss. On any given day, one might hear of tens or hundreds of millions of dollars flowing to a start-up company named Ublibudly or MeTickly. These are names I just made up, but they would make great venture capital bait if they existed. At these companies one finds rooms full of MIT PhD engineers not seeking cancer cures or sources of safe drinking water for the underdeveloped world but schemes to send little digital pictures of teddy bears and dragons between adult members of social networks. At the end of the road of the pursuit of technological sophistication appears to lie a playhouse in which humankind regresses to nursery school.”
The popular culture of the early 2020s—with it’s NFT Monke JPEGs, silent and masked TikTok dancing in the drab aisles of crumbling department stores, and rampant peer-pressured social-media virtue-signaling and paternalism—could scarcely be described in any more stark and specific detail. That such could be seen so vividly in 2010 is as masterful as it is dishearteningly dark.
CONCLUSION
You Are Not A Gadget is a special thing, a strange beast—as lucid in its first half as it is jumbled, meandering, and even nonsensical in its second half. And while the discerning reader might judge the book harshly for these structural failings, I doubt the author would care, he might even welcome it. Lanier’s apparent purpose in writing is to share his mind rather than please the reader in any particular regard. The sufficiently curious reader, one who is willing to engage with the book’s content, for whatever the book’s faults may be, finds a king’s randoms of wisdom, insight, and uncanny foresight.
In closing, it seems fitting to recall one of Lanier’s earliest warnings in the book, “Maybe if people pretend they are not conscious or do not have free will […] then perhaps we have the power to make it so. We might be able to collectively achieve antimagic.” 13 years on, this feels more pressing and urgent and true than ever. (Rating: 4/5🐙)
~Moon
Buy the Book: You Are Not A Gadget
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 5fbec235:ff265c2a
2025-05-18 00:18:55
@ 5fbec235:ff265c2a
2025-05-18 00:18:55In my lifetime, the only predictable thing about Chicagoland weather are its extremes. * Blizzards that can shut down highways even for a city equipped with hundreds of snowplows and millions of tons of road salt. * Torrential downpours that can eclipse 100yr storms and turn streets into rivers. * Blistering summer heat that can melt asphalt. * Howling winds that can uproot trees and make rain blow sideways across an 8 lane highway. * Let’s not forget the 2014 and 2019 polar vortexes that brought in -20F temps and -50F windchill (colder than Anchorage, AK at that time, trust me, I checked).
Most consumer tech would have called it quits. For example - My Kindle Oasis couldn’t even survive a period of non-use while resting peacefully inside a desk drawer. It bricked itself presumably because it couldn’t figure out how to handle a dead battery or maybe a corrupted OTA update. Note I purchased the 3x cost Oasis vs the standard Paperwhite because I presumed the kindle would be a no-nonsense piece of tech that would last for years to come.
The Vantage Vue was installed in 2012. It’s a wireless, solar powered station equipped with a sensor suite that monitors temperature, humidity, rainfall, wind speed and direction, all transmitted to an LCD console indoors. The purchase was as simple as possible. No account registration, no cloud services that require a subscription, no fuss.
Over its entire 13 year lifespan I only experienced 4 interruptions. Twice the internal battery failed and I simply went to the local hardware store to purchase a new one. Total cost of repair: $8. Then there were two instances where the pesky squirrels chewed through the wire that connects the anemometer to the station. I had an existing supply of solder and electrical tape on hand...problem fixed. Cost of repair: $0.
The Vantage Vue’s design is modular and accessible, with no proprietary nonsense locking me out of repairs. I didn’t need to send it to the manufacturer, pay exorbitant fees, navigate through an endless loop of phone support prompts, or buy a whole new unit because of a single damaged component.
Suppose I had not been technical enough, or too busy to repair it myself – I could have hired a local handyman in my community, shared a few laughs about the vandalizing vermin, offered him a homemade bottle of wine and a modest but meaningful fee for his repair. Then upon the return of those vandalice vermin, perhaps I would have learned something from his last repair and been able to fix it myself leaving me with a satisfying feeling of accomplishment... or also perhaps I would have just looked forward to opening up a new vintage.
The system could be fixed quickly and cheaply because it was designed with repair-ability in mind. Compare that to many modern devices, where glued-shut casings, locked down firmware, or unavailable spare parts force you replace rather than repair. My weather station’s longevity is proof that when manufacturers prioritize durability and user access, consumers win.
The Cost of Durability vs. Planned Obsolescence
I paid $500 for that station in 2012. Since 2012 I’ve purchased 4 popular consumer smartphones. Roughly costing a total somewhere between $3000 to $4000. That’s for devices that were each replaced within a few years of their purchase because the design and ecosystem pushed me toward replacement, not repair.
A Bitcoin Thought Experiment
Let’s imagine that original phone was modular and repairable. Let’s also imagine there was a functioning Bitcoin economy. If we’re imagining an established Bitcoin economy then we first need to imagine the irrelevance of the dollar.
The first phone would have cost, let’s say...10 BTC. With a limited supply of Bitcoin and no inflation to worry about, the entire world would be more conservative with their money and their debt issuance. Modular technological ecosystems would be in demand and there would be greater pressure on established corporations to create real innovations. True inventions, not just “innovative” profit schemes for shareholders. Technology would be more meaningful for everyone. Personal computing devices would be modular – offering local repairablity and ad-hoc upgradability, just like my Vantage Vue. Relative cost of repairs for that first phone would be more like that of my Vantage Vue.
Let’s Recall: * Original Purchase price of Vantage Vue: $500 * 2x Vantage Vue batteries: $8 * Soldering together chewed up wire: $0 * The feeling of satisfaction through exercising my abilities or learning new skills or staying connected with my local community: priceless
Relative cost of repair = 8/500 = 0.016
Now back to our imagined Bitcoin and #repairDontReplace economy.
- Cost of original smart phone: 10 BTC
- Expected cost to repair after 13 years = 10 * 0.016 = .16 BTC
That would leave me with 9.84 BTC which will always be worth the same 9.84 BTC as on the day I bought the first phone.
This is obviously a very, very imaginative scenario. Personal computing devices are more complex than a weather station. They do eventually require some kind of upgrade so that one can compute faster and store more data.but…Something tells me the entire world would have progressed much more meaningfully in the last 13 years if humans had more time to think creatively and not be worried about fighting inflation or beating the market. A lot of human ingenuity goes into algorithms that try to make imaginary numbers go up more than other people’s imaginary numbers.
This makes humans disconnected from their local communities. We become so concerned with maintaining a certain status that we might overlook those who are less-abled but still capable in delivering value to our collective consciousness. We might outsource very important responsibilities we owe to those members of our communities, thinking “it’s not our problem” or “we’re too busy”. It's the wrong mindset. It will lead to more disconnect, more chronic disease, more mental illness, more random acts of violence, and more children who outsource the final days of their loved ones to a nursing home.
Hmm - Maybe someone can build caregiving AI robots with strict centralized protocols reminiscent of those automated customer support calls we all love so much...
The long term cost is not easy to see but it’s clearly there, and we all must bear it. The Davis Vantage Vue weather station is more than a weather station. It’s a symbol of what technology can be when corporations respect their customers. It’s built to last, designed for repair, and doesn’t lock me into an endless cycle of replacement.
The #rightToRepair movement is about demanding more of this – products that we can fix ourselves with no artificial barriers. It’s about saving money, reducing waste, and taking control of things we own.
The Bitcoin thought experiment drives home a parallel point. A circular, community-first economy allows us to put our human ingenuity into the most important places. Gives us more time to care for our loved ones, and helps protect our communities from artificially induced societal pressures. Without those pressures we would grow more and outsource less. We would find value in those who seemingly can produce no value in today’s economy – and in turn we would collectively raise ourselves to a higher consciousness.
-
 @ 2b24a1fa:17750f64
2025-05-09 19:50:20
@ 2b24a1fa:17750f64
2025-05-09 19:50:20Wer sein eigenes Geld abheben möchte, macht sich heute – in Spanien - verdächtig. Wer dort eine größere Geldmenge des eigenen Vermögens abzuheben gedenkt, muss das von nun an Tage zuvor anmelden. Diese neue Regelung lässt sich auch nicht dadurch umgehen, dass man mehrere kleine Einzelbeiträge abhebt. Und die, die die neue Regelung missachten, werden empfindlich bestraft. So gerät jeder, der zu häufig Bares abhebt, in das Visier der Behörden.
https://soundcloud.com/radiomuenchen/barzahler-unter-generalverdacht-von-norbert-haring?
Was sich in Spanien an Bankautomaten und -schaltern eingeschlichen hat, könnte sich seinen Weg auch nach Deutschland bahnen. In Frankreich, so zeigt die persönliche Erfahrung, variiert die zu erzielende Geldmenge am Automaten unter noch ungeklärten Bedingungen von Tag zu Tag, von Konto zu Konto. Der Automat gibt vor, ob gerade beispielsweise 60, 200 oder 400 Euro abgehoben werden dürfen.
Hören Sie Norbert Härings Text zum spanischen Szenario der den Titel „Barzahler unter Generalverdacht“ trägt und zunächst auf seinem Blog erschienen war. norberthaering.de/news/spanien-bargeld/
Sprecher: Karsten Troyke
-
 @ 6b0a60cf:b952e7d4
2025-04-01 11:53:31
@ 6b0a60cf:b952e7d4
2025-04-01 11:53:31nostr:nevent1qqspynu0th85xlczqgnafy2na46mg276u0c5dmpd9utcz36npmqdmpsunn5rl nostr:nevent1qqs06cvm4qq9ymt2j58u0p7c46j2atxevjkp5vpezvlzesxcp7v03fqm0tp5k nostr:nevent1qqs8vjpu7wd5h7p0elysezzml7wzhaxgjwnp5h7yst0uudyy8pjt3pckcapzl nostr:nevent1qqswmpc5vghej8uz5mk8nta2szx3ejdsvdrvxtspmc3mld683j53mfsf0ujes nostr:nevent1qqs9cwaua4gvrxms3qz8rntj7jmuyvv953sm9lcwk5j4p8jfc4qxpgc7sfhw2 nostr:nevent1qqsx4f2m3njh0cpgqe376xpqde65ujq0aq50nj45ttfqls3yzluqujgpuum60 nostr:nevent1qqsrx7q02xfyak54zcmh233trqtpw725ywasfyg9dz08prxdvcnnuhqdnymnw nostr:nevent1qqsdllaud8mjpfhfzgu9nxjgvys5g08eu344909nyekrrn92pzhpxac56vtuj nostr:nevent1qqsxhx3skvs8xeddpwvhct3yhp02vgmdu90my67ttlj70muhcu3malqjadl5f nostr:nevent1qqs2k5q965ppnvxs7tna9wwx3njtp9r40ur4ahud8ykug85vth03haqe6m4py nostr:nevent1qqspzh3q002ssre56emu2kkhel82sd9j2sacd75fm998km8p6cxn8gg7agpxy nostr:nevent1qqsy8v9vj7u3jfnmhl6867n847d2gs7gpvdn5zdnm98nes9zlgu3rnqjkwmt9 nostr:nevent1qqsq559y4mj940540zhzxa9teknz74l9d6tqptste7l4lqu5yfvu2tg74dky7 nostr:nevent1qqs8gq3t2wk6qluhcjqy5cp8v3y20wmtw3uyfujmga7njpq3fe76pcgtgp34k nostr:nevent1qqsztaj9ut2lxru8la8lcs95lgyrpypwhgx92jc74r5nj7ss8tf9fvsr70m5v nostr:nevent1qqsghxwhmfywe40sdrq2cw750ug5f62nfh2u3jwe476zj6s0xmgcgpchj5qwx nostr:nevent1qqsdaw986p4qwujz99a0eg0yqtpjqhl6rcamxa0hn0yyg8pcwch6cysmans7p nostr:nevent1qqsyh8g0et5catuar388v56eahc4qmf7l6t79cs6scuuqa72vxj5lxq7de8wr nostr:nevent1qqszvxdc8vf2tjlayf7qf839p2j245nt7447ytqnju65s4ypz402gecrcsp8q nostr:nevent1qqspyx8mxme44n9vjspewch8s2tmtezt3z87kpytzetn68m39f0yhfsskl808 nostr:nevent1qqsdu6r2sf6npr3xn5gwkdc6st62zvy6r6r8u7sh078rjd7cjvy5jdcy8crru nostr:nevent1qqsrc0j0xa769ymehgxjem3lchwccndwj3ms922ltu7r7sy567lyzncddqjsv nostr:nevent1qqs0gcr269zzgcmrq6fjyzgqh7lqerhqqaknfrd5k563xnr9vanmtgcfzza5l nostr:nevent1qqsru4vxn5sw02zq4v44xtcpkt0qxqp9yc6gyy5pyavvvwa96dxyzscp3apme nostr:nevent1qqsp0ajlpxnvu64recf69efhxzv6sgu7yk235u59nj2v529dq92x2wgvcna9c nostr:nevent1qqsdmcrqmdkzf9tptgh5mytuan9q3ur7l50a5kjfrskfr54gxqq5k0szyhfsj nostr:nevent1qqsfk0duvuamrutcpansw3hqarnmhcr4vp0zt9r8pta9zlycma2jscs5wz0fm nostr:nevent1qqs82xxv600mtzxhhped2vn9yw7aer487ws8yy5hk5ppyuzxjw92hzs06hxp6 nostr:nevent1qqsfs96nd96mvulw9yp0dyygdtsegxkmnvytkq5xgmepkrh0504x0ns0rnm60 nostr:nevent1qqspa5f2fc5w4f9ghq2eryjnc44hs3grmaq6eyrx4s7ggkpjdmx2gjckswv0a nostr:nevent1qqs96s99kv7h207twu8s9mhmms7e5ck2s9qhndnp0m2w3uqpsh724ysnd6esu nostr:nevent1qqs8z5jzrlmeenpst0xtrm336tt0racrx63cnchskgs2d9cgmrtugdgmluxwa nostr:nevent1qqs9aqladqaf2jvanehny0mhd6mq9cdrgwr838z68p8h9clmcgf0zygqfvdd9 nostr:nevent1qqsd2m5tlpztgfqhzhc09upzzc876j6s60299m9lha2sxvnyjrvfasctaurj9 nostr:nevent1qqsg2yq7mw55vqnjmrfetc453v3z6vzzynmevt2ljgg4yppn5m2ry3ce2jlfe nostr:nevent1qqsr3vckac3re8ayyhv3m3g5s8a4rat5720un7qle8am2lfn7ew3magu6vk8f nostr:nevent1qqsg73fke3mszmuz0nh7r34sl3jlgdx70npfjc5almxrpycykhvnersq3rfaq nostr:nevent1qqsr73gdk6n0dgvg7nv6c390qf0c2j80t7qf99nftmze3dlr7k3nhpsfhl2ql nostr:nevent1qqs2mfw8a5vz3tjrnuerw6vxge0t6kd6snyeaj5jpfye7jvkqyqsv8cdw09np nostr:nevent1qqsr3qpal7xkhkttp4jrmjehm86ulh8hzarusgnyhhuf4ttdkqq0vhg7279w0 nostr:nevent1qqs0m4l3rza008tax28s3mh0tpexeqpzk8y2hlx2h8dgaqcft4rvm5c8xz2sq nostr:nevent1qqszt96jl70h9ku86s8mldsa8vk7m2vtwgfc2sksxcqfmkl2dksjntsjhz5zx nostr:nevent1qqsqdhulqcal3edfn2tu5lsj2tcgyq73zft3z6sa0xaqt4rd7m2gq4qpgs30l nostr:nevent1qqsygu35a9rrlh8ld5nuucjj9nw4up0d8mx6dmq98hqpj7j2kc6w7ts44y0wh nostr:nevent1qqsfnzz55mveegemu9nmqvfvm4wyarpevh29m778946lphw4wya23ms7z8ll2 nostr:nevent1qqs02ft4599adqeu9v3ny04k5x3mdued0rnj2hgg5lsg82xmqnpgxvsr48clp nostr:nevent1qqstkr7gr3flahhe9e6gl70sudqm5qz23rq2f2q9as3ys9s6l9c06lsgrduvd nostr:nevent1qqsqzmjj8rn6pl8wrn5km7an00cfhy5wzqzz9nlne5hzhktwlnsp0ag0qd665 nostr:nevent1qqsfc2x5vx23yyztnvr3n59dv9kyw64jc88pxxfgawt4c8m32qq5ekqqe4neh nostr:nevent1qqs0f7fkwlky42jxsdgr33xttz3rkg7gk200qkmv2rulrlauqwee7ts7mzn5q nostr:nevent1qqsg3c8qyp4n86qdtkyzcnk6kr7gnmad3sd2vhel52m3r64ala9rqugrcnnv6 nostr:nevent1qqsw9dn2cuhe4xu76z2xyugh8gaah92rdyazyg0s2mvkll0qrll02gs4uvvvk nostr:nevent1qqsv0pymkvfqz53jyqwqjj5wypp375ljlstav67zzpdlq536xpm8d6snawjc0 nostr:nevent1qqs20fpumlhmzs49mlsvd2f0s7kfgjq68auzkfvf6s3yr7a0njy782qv778m2 nostr:nevent1qqswqq7pl8g5redm0t82k4ys50w65z03m5xl6ayr374c2vknqfwjcrgguyt5s nostr:nevent1qqsp0fn3adqdq3jvcna0vwkwjnaq32lx6ac7qzpquvdt8zpugx5gvhshhkgez nostr:nevent1qqsvtd6surkas9nrvnlndk3r53aqq82dedmm8ayf2zhrv9w9lf90g8gslhagd nostr:nevent1qqsqw56qfhvkv56ss5r066yrf2hnwchcn4ldav576ldhvk3jk543clcsayyfz nostr:nevent1qqsxq9faxju2wp9zl5gw7usu00rkm7n0x9ylnlujsjjn323wppqpausm4etyu nostr:nevent1qqsrl7gdwgd5mqf3s3ygn2e5j34qnjxeldr99qwn7lge3ncfdwhf4usl70dm2 nostr:nevent1qqsd2a32drg7teet8fnkauxede52lyrau8ey24dzzqflu7pad2fhsvsdgtyr4 nostr:nevent1qqsv5uqj4zxhdtdapzk44tfuxyft55tlp900r4l7rf9vtma8d6cgjms2hjwde nostr:nevent1qqszcepleg57p2k03e06et848frekk79x3f523nmx8t3guxmuyfgsyqeat4pt nostr:nevent1qqsvklay6j4ukvc0w9n74u5hzselsrmclm9jfmezrztqf3xf74522ac0rlcen nostr:nevent1qqs909ldkkvchacs32hpj4zphwxdyxtnvv2nz0wdk7d26ec25j7xyfcsx997r nostr:nevent1qqs0nyvnc4j8xen06z9t784htam8e9jsucpm7g0xq2cdtenxrcx4qdgmgtj8q nostr:nevent1qqsfq3gqv98x97s0wu2cyenz5ng0v52fsv8erzyuj8q7ls9kwaaafggwt30r0 nostr:nevent1qqs2pu4lcqakjgkx524jvd967vk2fkuw6urtp7tw38q3accra6hf0xqd99kc3 nostr:nevent1qqsvgwlfeju2qsnllqgexscdrta9lnqamxlq2kvansadmhyy0g0eqhg02dpeg nostr:nevent1qqsvveq4k9cz0t3xh55cudydkweh58aekjrmqh6zut7ekqsnuv3hfyqdrru6x nostr:nevent1qqsfn29l63mfggnvq2j3ns9u09su2zrsahrxmczh4mk6q8mq45lxkps5alh6e nostr:nevent1qqszg3s0jdwj4qug6plqe865ul8zh6j60gue9c5f897dclmvu5xc2zqv77xmu nostr:nevent1qqswla2n4l5cu2z3czyt8vyawylv2hxj2avjg0lx6lnl7cw9p3kn5ac9nf5u8 nostr:nevent1qqsf8qufcluup4tl8rcngu5z8tarzxl7the3wfe0xnfdyjht9rzvpaqyzcn57 nostr:nevent1qqs8turf9zhsjc7uunw8wgqtd7dc5wtlrgxf2wrvsnw2cgz534wd6sghzcgw4 nostr:nevent1qqsqwngx9nxgf7slse6yeh9uvnpmwz3exa95qyh6x3ez00z72y2jvwsrfqdhk nostr:nevent1qqsv8z7leemtzl5cfexxynl7243uqd4nr7kacdaumyx8rq46kune2psgz47rc nostr:nevent1qqsp0ttn3kcnds34zjew7w7e8hwnaa8hwx29t3tej2guawf8pdt9csgz4m9nv nostr:nevent1qqszy0yufenkexssavnv0p5k98e3vu77f4r4tze5v6p94gmgcrgpx4qd27h77 nostr:nevent1qqs2xj626q46rpzwnas5259t5ywpwzltnvj3pwvrjcqseddtyu500qg5rn883 nostr:nevent1qqsw02jdkpg2vzs5k5c3ymvndsrkje6uwkxf0dqmz0yvycfwt6lvq6qjqgfgz nostr:nevent1qqs2d237yzkmuxl82fc2u7wdpzxyvjw2gje6vgadtw4dzmnp483jgrcval8vd nostr:nevent1qqsrwqj390vqwp7e6nwu3k8m6h4luks86gq3sql99k5tnvy4w52kamqp73nl8 nostr:nevent1qqstdtqpxl78ecn9x8dzylvzul0cfsxh64gfunzts72l3sqmvzt0ylqwp9c8n nostr:nevent1qqswcvajl70frlhwtuch6cwlsehl0u7f2hfw27vhxvzwhzatm2ugjss4zle92 nostr:nevent1qqszfrq6zdsclykmeke3a7znqgp7y975mslf5w0fk0hfujajj9jh4hssc4s7f nostr:nevent1qqsp253cwmp33yedu7asa6k2f09w08j34zcky52ks6jh97msqsrh9nqylwer9 nostr:nevent1qqsd3u0gms7u8gqkvhpfqlvk2jrttjzs5zuvc8qdl3g5pse4dt8ugcsqcez79 nostr:nevent1qqsxq8t0u67schrxvv0dtuf2j6nlvqytkez42f0jmhpjtnkap5ssvsgm7pdcc nostr:nevent1qqsvp878n0zlqkge6famsdwcqp8k92flz2wf97c0emxlsrf7f6gqt8gyzkgp8 nostr:nevent1qqsx3xnxupzzfvws2etneycjyvcx0n7mcqru09gyym5x20s3n9ewcrgcsetd6 nostr:nevent1qqsf666tlstrgssclusaam50nfk0xjs7m849f70fuv5hw9h7tsmqpegaduhy9 nostr:nevent1qqs23eqhwhvah5yjn54m7n5klw4e5efg8s6994pamz5ejcgnsq4d2wss89y7y nostr:nevent1qqs2q84pdl6qvf8h7yu9g6hfvfzj49z28ea5m6k4lpmwvl86tnuedxqkxxajr nostr:nevent1qqsyf0quzl6ttedn7qftse9386uh0pvp8795egxumyvs8sjckm8xgxs2srhmy nostr:nevent1qqsf7n8rqr2wsjpcuczlcee85227rylnv0kanj4mca0hllptyerd8csnyspns nostr:nevent1qqsycgshmjcqsr76tlhuppp23a49zy4e995lj5wnqm8jkz5vmv9l55cjpughr nostr:nevent1qqsp4vwephtxxlv2pjgupymfl6k288qh6gdzsy8qesmu0natsh095tsnfrpnk nostr:nevent1qqs297q9e00dpmj78rdx2qrjg3hva5ye9p7nke8avagn844jxucudwg2mtxgq nostr:nevent1qqs9c08g0fxv3vy7v5c9gsme0jx6fujkv88k3rtnmxjcd89ejpy72hcadrjas nostr:nevent1qqsvmwsetretl7dm42c3g690llwylyn37cunkauepzj3le3qhaytrjsh2ga9h nostr:nevent1qqsgyqu6zjppqek23fgpzlmg7hqfl4knryjvuflx54ypx70m58gt6rs5s9dms nostr:nevent1qqspxcsk7g56qhapmzek243az6zhv9v5hwupnyg4nn352kvc2z0fw7qklkcv7 nostr:nevent1qqsxwe7u49q4yc4ney5kt6gkfep0v9jlx68r5u0uf9upl7u9mcfxpkcqpu7z8 nostr:nevent1qqsrmyeh30f4kfdleq23w9vgcx9jcqgkv3stg9au5m593tlywlca0lgylty6g nostr:nevent1qqsg2v2e7tthtd8m39ctt7yyqw0lqkx23s7e2fqt4s2ymlnn33n5axg7fy4da nostr:nevent1qqsvtgfln33c2nllxt2797xfqttcuy6qtlh8we8q9lv9gn7r5jy4ahsfqpyg7 nostr:nevent1qqsz2al0emnaf5cjtrtdfv9c9t5ey8475yx5kp5442cg0afmlys6dgg29jq4x nostr:nevent1qqsg8lvelaeq9uyv7hzrxgpelckuz5hpf5g3ajyghj8nsk2ycckv63sllv797 nostr:nevent1qqsxhp4g53ltg7qjz2puzvsdwxk54xev46n8jmc2tlg2pdp529ckgfg2329m7 nostr:nevent1qqs82j5zgk3plkk8fugmflertrl8uc6x36elfeet643npvyuxr39tvcrr2u63 nostr:nevent1qqsd4vye657t504chaqf2d5gwgd5946t9tfg6aq0fnkjljnnmkfmadg3ss3uw nostr:nevent1qqsxhr5lanyrce0c6amgvxzd77a26fpap505hl74jztuc5svst8dtrcvtcl4f nostr:nevent1qqsrdap3r0ptlwxgd0dav04y53w04x0jzh22d4sxksuzfpetf6j8zwgtmay55 nostr:nevent1qqsvyqj4lr5g5swahxxjrpmga3569qlmd96xk6f4xwm84gmwu7aqw4c69zqtx nostr:nevent1qqsf9dntcjdmmzsu0s2t7pnlx6ver9usvaz53hvgtjggfgn8da6eydc7l5gc2 nostr:nevent1qqs9njwwgechxesqycm29asghutvq0e2fec2v4jc0gvpsk2dsnujq8c9vnuuq nostr:nevent1qqs9ahfkkycdlkemndn0dc7am5djnp8pwjnu72sng2tg0pk5kq7jv2skfv95c nostr:nevent1qqsflgngaeu8w2xz2lkzly5rvr3rudcvq4yyrn2w724dlr32p2mulpqasv6vj nostr:nevent1qqswg7qfwtdj38kr9xfp7f6gfvaxm5kpuwp22ueqny5pp6da7snl92svggqww nostr:nevent1qqs256vewt769a0q8teqh3n5eggjvw0jddl4xzejx4rykhcrrx2k4zcr70g2w nostr:nevent1qqstf7w5lej9qqm63x2r9c5ztc7s9tre65f3e27p5mhqjzy3555856g0lptxq nostr:nevent1qqsfzchhw84ldh2egvqethzychr8jvaaurdacvav3qhgelwzldy7adslwelmw nostr:nevent1qqsqy4uzgsedu94j6jyjpavrmn35khc7nsdmhxnwqehy9umdkgac79skwad40 nostr:nevent1qqsrzxkswpug72gc6eqf4qklemc29quyscds2ftwuqmf0lwvz78fckqxq9r9d nostr:nevent1qqsfzvl36d5k89q0frn9gfepwjrd65cgarh3gtj6gmqffjh9v7ncpesfxuyug nostr:nevent1qqs9vcndnjwtjcg2p5yj2jcktscn8lyf766kqtjef2a3fmyhsga0mgg6d5vp7 nostr:nevent1qqsdf65dzcvx2pkwh297amygfcdypu80g3hc2w0hzl6l8ed8ptcd83ccux9kt nostr:nevent1qqsr69tp6y6dj6agued5vqvv8wrhwngtl9nk6yln2amzg4j0fnxfsksj59765 nostr:nevent1qqs0jjfn0tnjgvech67ks5n3x9zrpredskg67twea7m2x8hvuq3zvvsjdgjcx nostr:nevent1qqs8s9wuwnqmkdjwmrxmqrjyktq3egkxlaqzx7t6q9e53yalga55xuq5ez8ug nostr:nevent1qqste2hugs0txe9xqzle5y60t2m5sakxfcq4flw9e6gtxvdlpuy2qqq3ksyc5 nostr:nevent1qqsxrns3rez8vhnym5qvqkg434w26r2paw8jm9640lzmhzs7jc00r2sk5nqq7 nostr:nevent1qqs05du8xmstnuajfj6cqetxv06xk8xgj23eepfpyjk8hdz3v5hx3hqg7tcwf nostr:nevent1qqswq92249238q2gp6cjcuup5w0e60htyqrp22cepc6uelysmewp46s3n3c76 nostr:nevent1qqspwxsck6zz60gc8tr48l4qqdnlnva0s9gay2hmdckutrz5sk8mnpcueftjt nostr:nevent1qqsywqjwwnuycnzkar8cnua5lerl80kr9wvwdr4yy07k2r7enlup08s0w3tg6 nostr:nevent1qqs87m5zz4x2cctfvxrvxx9546fe9rl5j82dxcrz4s89qzk47huyalgrd3rk7 nostr:nevent1qqst7lun76xhcmaw84s7cwqu9wu5dfterxxhjptlw54gxhnz5duxcaceaky47 nostr:nevent1qqsyexk849hlfxhnqlt4t6y23jshgeevrvtu53dh95w6xfeuuxrvz7c2aj87m nostr:nevent1qqsglmpnfw3jgl9ekwanzlgzhndce6pmncvunkswpc3y2n40vu33m0cwds2v5 nostr:nevent1qqsdaw8rm6yww2ks8300m2xw22c8xdemnkspdvwrjh2jn6hnuvuh9zc6quvml nostr:nevent1qqs0p6d8ny8kunevc8capqu9ntjmd9ze24ql2sjam0j0h8ju0xjydygkm9ffq nostr:nevent1qqswu057ppwc2lars6nu8sc8j4rupnahsrn79a8zktsqawq6p5fh46s5t4yqn nostr:nevent1qqs270vsqqtjwjyswfmqyldjnmnvrrp5g5q7wh3k5qj8cuhljwn0j5c8md0u6 nostr:nevent1qqs2ypcx6p5cqe8dqqmrm36qvgucflgvss885r8czcal6zv0axqdr7sn0x2df nostr:nevent1qqsqvf477f73gm2qfkuly89sy4sadju6wh4t6dcqgh4zwr8ds9g9txg9gppkp nostr:nevent1qqswnmvwph8x9xnqr4n6ytxnfz8nl89a7hfrk2453ldxudtql3j4yns2fj3hs nostr:nevent1qqs2ecqgkcgmlvzj90c8trmw3nld0trtuujnv28f5ezt3huhvvtegmcagpf0y nostr:nevent1qqs9s9zkznyxu6qk7svajntw0v02ldr8462dgt7n5f9slq7aleycsusl96zph nostr:nevent1qqsp7nux9qjzsx4ypcrjexrz25clr9586ar5n5ahc70r7yhakzvaeasd63ulx nostr:nevent1qqsp5gp2xg8lx4kneqrhv990x0velm85s5u2jmggkwwzt8yrxygdc8qgfsp3z nostr:nevent1qqsxdt30myarjhkprzt8xx4kfy7fhyjxshaza0z52nq0pkgwkqguhugt0jswa nostr:nevent1qqs2qq3wpva3lt07xrde3y2vehqy0cwyzye52cvhjnlyw5x3rghsgrq93jycs nostr:nevent1qqsw0959762aa5pxz9hhaa6saszqrnqjrr5umtl5kkj00prqka4fc5qnpfek9 nostr:nevent1qqsx5htpawdvx500074r0skyxhrezkfs7rctuu4afp4puykuvth9kksr9dc64 nostr:nevent1qqsf7kexs3s0g0f4dzv9c8qdns6jh6e26qvecu59d579ud0fta8a7ag7pss04 nostr:nevent1qqszkphl8n8vtgfnrpkudwe8nsm47pm95ajy9a7cdaz3k7shadjynaccpqzv6 nostr:nevent1qqsgrperqd4nrjegephrrdcj0qwkk22glfeq3msumte2evup3f5f29cv9e5vq nostr:nevent1qqsqueyp46tjgh4s6fc7af8r6nnpdetrutmemalfkk0ruqp93zt4ltc3hdj29 nostr:nevent1qqsd34zcm5gm0aws879q9t7sdm7r7rvd75sj4uzxxslwa25ffay3pnc4x9wmg nostr:nevent1qqsz233vcgpjrtkn03kh2wv93jwt0m042jpqp06uank9vfummhdrqxgvq0hnj nostr:nevent1qqsxdtchwzjvxvml4h27ta75542vgc6zpdtzeuma4hrz55v9trswdns9dpxna nostr:nevent1qqs922qlylqjrmr3uaj0f29s82smytg67cxcl208memnktx4h7fhhxqd2wzwc nostr:nevent1qqsrpzxupddee90chcj8psnlhhd8s2r68tvz5u09u7u46wj5a0hyyvs98d2z7 nostr:nevent1qqsfkl9ukp2gss96ut95rwyg3gfcdft4qnkzjc6mg2x4dnpxsezwx3g7dl4fg nostr:nevent1qqs03mv7zygd5stzm6mlh3v57mszuhvnumwfpa94m2axlwqhrtyjfacm9hfaj nostr:nevent1qqsg0k2f4l79804jydkq3ryekkjk95rcysswg02ktrg3cftwq5jnvdc6pcn0x nostr:nevent1qqsw8fnh3x09dj7m4w0engzftejh5pq0dgjzcr23erpg38kyvgz6taq9hg083 nostr:nevent1qqsycaw0y5z5te9r8m3sx8cngczuc0dtzcltf6khwgwhls4y3vxv7wcehkkgx nostr:nevent1qqswpdv0jy9ag757st0c29efprl6jttz3jvrgaxg382txm4r38shhcgfnzhvu nostr:nevent1qqswzt4yac0p8536j4venvexgt03shq94xnsp7lmxuy0vq9wl9dj69qqtr6tg nostr:nevent1qqsw5p0cm9wxvwjlv3z2kewze2t4lw073h7x5lql0g3az7h7jnd0pagxxsmwp nostr:nevent1qqsz92z4pa6zdhhchrygypy39x3j8u4mv98dflxmsw39dyuerfgy2xsp7rg2g nostr:nevent1qqsqur6s28xh68lzft7k6suklrv5knjp4hysunyr7g79caucc8vt7yq6kl0zd nostr:nevent1qqsf02sunq6yqjcpjlm8a4ku8txkyte68gmtvmhyez0lx424cxk65zsv6gk3q nostr:nevent1qqspexe5ew6dt7g3ps9tk2cd345y3jd0asfuyj8pgxv4m5ywqw990lqyhzv9m nostr:nevent1qqsyedkwvv6u4ludqgz623ftuj4mncn5c3tzf533q6xgc4k5xgn435s62yr3l nostr:nevent1qqs0qr3al6we2zeqr4lrkz6nk9cp7cvf9ymt06khw7d4377k7ar5n2gxtem3f nostr:nevent1qqsg5x0qrjk38xpmxh83n2wspg32gwwr4hxqjsc6xz60wess9efy4eg6cpn6v nostr:nevent1qqs9swl3twdd9zjr55gsq43gctczv4cjn0an58gn83wf3ujquu0l7lcff4ma9 nostr:nevent1qqsv9sc8m3e36a253p4jg5am9ay92ncjnx9nttsh5ss37ndr4znu97g0lg0hz nostr:nevent1qqs90fava6xzrjhdpkwld3utw3xl6ghddfmlu9ceql8p82mkv6luvwswptxe2 nostr:nevent1qqsrx0h5jz7vjv7ul0w30rjqzg0eey8r0ff0k9cf8jfcjjr5a57kg8s8tz2qy nostr:nevent1qqsfwln27aduh4yw80cqwml5f7vh5z6v7q80gxmrv3a97x8zfw0a7us40qsmx nostr:nevent1qqsyyl03g27p9ekau4v483800dwc02sfeay8txxn67mr3h3zt476sdqv7dc0g nostr:nevent1qqsgup96lkscndr7jdze308kt495s65uura9vjl8yucfcd0depzpe8cdvlxjr nostr:nevent1qqs0c0zwxpfv4krj0vfku448tl3jpudw56nw4wr4whlje7cexauhd0g6zqjxn nostr:nevent1qqs0dvc82lc2mmzvkmqtcua7kt0vwz4am48kj9sq0rk8xpsxjxw5pgg4qe329 nostr:nevent1qqsxzttj97g67mag82fww0aglmvt5qwvk59e7euswn3nmjtpx5j6thg6c3nz7 nostr:nevent1qqs0gxfve8yz6m93jaseldl8xzhsmpt7k3gkqlv8xlje4q6aqjnna0gezcl83 nostr:nevent1qqspj6puxtaj06z2shd9nr82t2rwwmh6mszapee4gjyj7vra6pwfj4q22x99e nostr:nevent1qqspcrj2zg0jyy7ardz4kt4d5n95wz84jl65hmrdxum7nneeglwtnzcxxzdt7 nostr:nevent1qqsd4ddx493uj3wuxscwfjl9le3f7t2f78yh385666knu26vr9luz4gwa0w24 nostr:nevent1qqsx4w8ztgk5m3wz59mm0sqr7nyzx9hzu005vae6kqaepnpxqw0svwqaq9le0 nostr:nevent1qqsztgtzz4nqf8znh8u3q5fwtnx84mzrjur8gq6dmg3mj2kn3ugx2xca4g2nv nostr:nevent1qqsv6m42nk6uerh02wnflytfvj4nuj0sp43s9lzuvd5thprz9k7jjgqgywnf9 nostr:nevent1qqsvennjay5vvk40t99jwnuefa4lw6zuhya4mg74fsd0klrwyfwjjus0atnfx nostr:nevent1qqs8awph7hzu76df5w8k4xx6j5wmc8tnddxa4sfwnuruea78wr4tg8c47rsa3 nostr:nevent1qqst2222z58smd36lltudxlme8fpyupg8t2c34z803n668t5pmt0ypgsv3ryg nostr:nevent1qqsvjphy6fz8ae244jzdha9xxmz2jcy0pz6zfcse626t9ms5xlcyeecmpdyt6 nostr:nevent1qqs93ghgzxt4ywr404yn4jm5lx8m7l964mmgqtl55khza7jfwsk3klcyup39u nostr:nevent1qqsq0lhuuwewq2kgtjk44z8wnuhv9x0lrvym08dk5p70zk3l9gupp3sv3dlrp nostr:nevent1qqsyq8u0tnangar2w7ft0cfzwglxmwk7kkczpj8k7wqjnasz3sq2sgqssvy50 nostr:nevent1qqsyh3f6lhft7mxmf57v68ypfa4j5fdkuvf43c9q0g5w83jtzwsg86gwhjqtp nostr:nevent1qqsysgrlqjk2wayzw0dymw0r0wv30lk0c5qeagc8h7lmulyffj75clg4t4anr nostr:nevent1qqswcpe2hfr6zk46p0jv65kl3wtp63smv6uxe6j4evsav9dlcpe7xmcx9kqrq nostr:nevent1qqsxv5tuzmfjm3dcz05xng5e9gl6e7vqx84h37p83d6qstzx3hwqwlqtw59hv nostr:nevent1qqs86k2c9akxtzvw7upchwu4pnesj4ds3d3fsg8m76mjdpvj38zwcac6vud53 nostr:nevent1qqszltfvvs22flkqd2v9jzuu222nq9jud78z5sjk8z6y7jmqnd3f3fgme3yek nostr:nevent1qqsrglucq53e84kgkaa2hsq6a5xahraethlykzx6znymtg4gvxenkssx4un3a nostr:nevent1qqsvaq0lwefwnrfkvmrul84fneecua2g7eg8henlkuht0r8u0sp79cqqwt7s8 nostr:nevent1qqsfrah0av2l3dc7valuqklryz2a687t7cenharuq7r6xelm0e0yv4s494vpz nostr:nevent1qqsrt7uykaetqwl2q90x6kd5xhgh6apn8kz7gvy6hgsa42xe6qmqgxcmyll46 nostr:nevent1qqsgl80erg8t5cqdz3wnxzd2g6ekhdtm7rt3nxszzvzxft7v7x8lqgc084p04 nostr:nevent1qqs8gsthklfdzy6fku378tf6807qk86kjcgrgaavrjtdffh2e57la8cwltl53 nostr:nevent1qqswjgler7slw0lncaxhtne5kz3np3tu5umdef2aqavy5atq0tvgm9gns8h40 nostr:nevent1qqsr2ka8n6zv0z4mk6ty9nztqd9qz8rkgt6cjck4ce6mtpm8sxupmsqj7s257 nostr:nevent1qqsrudy60t40q9vup3p0kxrrnlllwnwnyh8kt4x623d3f74jctpnrvsmd8zam nostr:nevent1qqsqskyce40lmwc9v94tkxy5phnzf4p55q090g02wt0x40czw8mkk4svtu7a2 nostr:nevent1qqs24dsj4x02x80lvgtj3khkcqpqv6qyypfse2676et46phrztxs75shwde3x nostr:nevent1qqs2cyspyllevj6ahmzep5jhlnnfc8448uh3jn5m2qfmn8y3dma2qggcrtvve nostr:nevent1qqs0k044ntscwad95k8347wuflpchrl0aszzltfyp2nxpv3g6kr2cass8k459 nostr:nevent1qqsqq9cce7umtkm9e3588n7nl4y3dktlskssapph5z6004hqg9setaq4zcqr3 nostr:nevent1qqsdsxzfqhwxg42a652t4234z7p703lwrulfnz9drsus8erjvnag74c3606pt nostr:nevent1qqs0wjxh4ze8xfk7sec3zu4cepwtwexqty80qpvp5nxxgvutk9lqydch9jzp4 nostr:nevent1qqsgavz69cxs6mx2y42j4qnqn7q5xdwvmnaae2tj2px8zdep0j8rs6g87hl3t nostr:nevent1qqsru6z84jtjmycunulyzf5ns3rq0dweseseyq5rxmuzvcs7ylenu9sykk9re nostr:nevent1qqs2kxhn4sl0p8wyxzcv4gpqqwztky37p2j22qhpjqgn0cy407yn03qmsctfx nostr:nevent1qqsf7ug82cd5c02jkm7uahc4p7kc8j32q2dgvuun46ywmlfmrwu6xns3r0egn nostr:nevent1qqszckunp53566u6grgw75gy2c9ce6902zd3jp9cfg20paq66lxxdjs9l259l nostr:nevent1qqs07qw0kashdjyxgj6w92p44hnd3l9jeamxhc63fkdz9cr8na85pwgqlset5 nostr:nevent1qqsga4g5haatk09u4vkm6nfmw6ngctg6p5jzam5kax27lcnc74vcsdc5fwjjf nostr:nevent1qqs8uu57ukvxfvve900uvynudvazpu8xuw7zvexkctm62rdgtpu600qcdwg0y nostr:nevent1qqsgdc297tvnh06kqrg3e68ftyu6prwjqtvxj782f549jugart2jc5gqcqjyp nostr:nevent1qqsqkus0qg7nnl5jkjzhugjpd6vfn70m0r7xtpyz3mhq9k49unuwg6shprvut nostr:nevent1qqsgxaedjvy4s3rlfg8235c7yh0uxc0e7n967p9j6uuz90tzvafzy6qrmcrwe nostr:nevent1qqsv2j2dchuyajecmrqxv9pra3cju03fwkes5qy3xrjtf55twjmx64cjvx347 nostr:nevent1qqsqmnnasdsf5zmqlq3alycl5r2uestvx5mshvnl56fdjk0qx4t2hkgnzn7ww nostr:nevent1qqsvdm79znu685uehrmmegcmq836jj3qeqtym8cv356wx8y5tscjg9c0dvw4y nostr:nevent1qqsy8wx4ujy7z3e6svmz72zaapu7xqx7y4xsuthuk6ynwkzfl9u92nsl42f8c nostr:nevent1qqswccl50t2p57wdfam07p2lvdqzxeg6dzm72vrjsf0xjl88uk03m4gzx25jj nostr:nevent1qqstv4gslzxfte85yckx07fdn5phluvcnj7a7pf28j7hgthkngs7fgqhl5fay nostr:nevent1qqspeada7h3749ex026n4gp60pkv7rtt5nzn4p76dyz9vfzyhxp5puqw6uech nostr:nevent1qqs88tlgk2gd2dsf3mre36e5nurg8afmynkafwlj59p5295wq2dycccjtp7l7 nostr:nevent1qqstu5z907epgq3rechx0ezqyge3uj7nm2j2ty93hj9rwuxxzrljffc4zr0qc nostr:nevent1qqs2r67wggz466rv4kh3vrhyl8e4t26a5s4tq7wgfrglghnhcw47n6q9mhltw nostr:nevent1qqszerzkulum87k7ykzzg0t7wa2lww8ttt7xlu6m385hl5p07lsk9ych3s90p nostr:nevent1qqs804wfmxcdt6gev9qmyasz7mxq6m8k287ulsfz39umqcgpqqf2jnca7xk42 nostr:nevent1qqsgusg06zl58x44778cskde5n8uudgwwajfdq28nvq38kt8nwsyu8qyw6hhx nostr:nevent1qqsy8ecclr3p6s9r7d0ge060fsc6qveuj8509nkndq9stzp4aslejuqw9j892 nostr:nevent1qqsyxns5ze0qm54f3nhpc0dygqnq60e2nmmgpvlhkg99zt2fp7umedc7latuk nostr:nevent1qqs27g6c4vaqxkc2gvnvuged60095fwdsk4e4ze77ylazg9lgz0mlng67q65m nostr:nevent1qqswcy0v5pn5v9wx6uzln6nr4nl4w5d0c688gx5z3qhepswmhu4zgdcrvux38 nostr:nevent1qqst3l22tc9thmnks3nxa9lqdtejktk44ved3xkyqy34dzuzcz92npcdvgtlr nostr:nevent1qqs0jnryazxjjl8g3hxw2xh4fastfy9cu47lpm2qgh2fc6tf4d78sqcphuvzg nostr:nevent1qqsva8k2qn9pjm4wpg879k37f9hxtrpa6twa4ck9uf33e4udzq308rsavs72j nostr:nevent1qqsggahcy8q0zgyvjdpxpljykjahjsx4tkg7z8qr6m28y0hjvfkredsyu0tfj nostr:nevent1qqspayr6m5dcevp96sgew5zn7dye0gm2lrvwmlhr0nlv8kcayarlp9qlntm3p nostr:nevent1qqsdssqj635ee355wdugls0lr7hgfwjjxdzr3appz2pc0wrsp228wrghtxuzg nostr:nevent1qqs0end22ejwqry63pt4yq99ez2jsxj2d35kpy3dfnkmsdx8pk53pjcw2qdwy nostr:nevent1qqsw5t6gr0svp9wefrve6przj6hqlkp7ma787ac8tauxwtc53ws2a8sru5vm9 nostr:nevent1qqsr53vq37g7mm6chgsafpgn9hscgaku6m00mu96d05lryqx285k0yq7ujhye nostr:nevent1qqs8w3ds968pe2jeazwt3ra5y6r3dlgxqgt0an7fd0zy7wm2lkgc2ucahcjqq nostr:nevent1qqs26szux5exxukg7ht579uytrcs72j2j9h2xf4dwvz044jpntsynagqv9sdz nostr:nevent1qqsrej9r6kazt3eda4hhu70tkax4j5ft9l3ve4apnh5u8p9ltj6allgmn68a7 nostr:nevent1qqsq64h92pdffc50xvmlwdfyms802x029qf5pe8fwlu9n4v4rg93t8gfa7kee nostr:nevent1qqs8hhmaww599xz682l2hx0uvn4sfluc6aa7lydk4nugxejqjeaqeugyg0glt nostr:nevent1qqs832edsy9yxhq765zfummutc0r54zc4xj7n9lcuwcf60c66q494zc7tlqgx nostr:nevent1qqs8etkcd8f2aw2s7efjdsj8w5ch8r8ej9capyx976w343ps9sm7s4g0l37gr nostr:nevent1qqsfwaetdhzn3z6fqs50usmktug5v4stcet3lus70p5hffjq8kcpuhqpu5ef4 nostr:nevent1qqswnvtzachtgqc9gwqvcu4s0mtmwxnl78v544p22u6cuud95s2jgmgaz5glx nostr:nevent1qqspmckx784xjj7mkn70tu6rfnyq0kmpcg4p8jr6dmlh98um8dcqnvgj8n426 nostr:nevent1qqsdxeatzq42tstmculgf62rhj84mpgfzsa54gjsh4hrl6e64jv3wfcvr8fec nostr:nevent1qqspcksa07zqnc0xf9h57mpvna4ke5fd5g8lw0v6wycf980lhh9fzes3k5t94 nostr:nevent1qqsy8kvy6s5spzhyfjvj6lzesj0ynnp5d30pqzuwe93d2t3xmrl77dcjz5sfg nostr:nevent1qqsyh342up3pkjfkvzr0yjaxtu4qg5syquz93xyd6fgatdwqxy8e7mgklaf0f nostr:nevent1qqsyp94g3puhpz0k9vaft8tvpqew024n3asxpklgnax6fdsu2mu4kcqkq7fqz nostr:nevent1qqsznp4zqx06tjmplxdr0q548f3kcn7pj4hvf4g4rgm74yk62c59lnswzsdn4 nostr:nevent1qqs29ffntcwt0t5zv7ecrzjgpd6v2r0nqwg9ymm5luhehgrzhlr4f4shqhwee nostr:nevent1qqsfrn6h3hjk4zrs6pamcdzapap0gvemrm2akxlur005chgh4vaps9sx4y5sl nostr:nevent1qqsql32xdfshaa73ex68fz8e4r6e0lhpcgsgdhczwfsq6e7lqqt703cuhue8l nostr:nevent1qqs952dv2ycq0a2tdvyj7st7sd87pxzh7hceth96hhhwjq7gs95m5ccdf764h nostr:nevent1qqs29kzdduhtv7v2gr40nhzkykls6pwmn9maspl2qs83gqkk23ql42cmxwq3n nostr:nevent1qqspwpz06fysr7xqyjfxg296e5d7hcycp3wkmladpe39tkwtmyyaprgycny5j nostr:nevent1qqswsj30jgpyt623gqpy5gk434xeff94cwqrpzpm2tdznhqlvs6dghcuxdx4l nostr:nevent1qqsvty7umlq35gydcj4n2tmzv334yuf5dnw9p662q22rzfq5yhwpk4gz7fnyp nostr:nevent1qqsppkpezwkyfezakg9se8uzvx8j6z33e7k3f4xrpad378m5jua5z4cms7k8m nostr:nevent1qqsykvscexq75xect594xvyp0yzlstagqa62kmpwr94wl7q0exg8h9cwfxcmz nostr:nevent1qqstfqwlc8rmrqrhdt7zdd082eehssdt4r66h3j3ns42cxvnzjegfrc7qr8wd nostr:nevent1qqs0prhhhyvtz3fwwsu93ndvc6ye32zp885eyg6rkxldc37f0jck2eqe3kqr2 nostr:nevent1qqsvr4nsccw9dehyettdc0tr4t3yycvldjxka6cte8uth5r6xz8vhxcat20d4 nostr:nevent1qqsfkxvh4h3ga60l3w3x5ngu777up09sxrqdjgkrnv3yzdhdn2ljsnsylcsge nostr:nevent1qqsfc83pkdtd4jph9r4hjyc4xqczdcem3ytkvp732zalqkl8jhxaq6c26cp54 nostr:nevent1qqszd2hpl8h2uljcgqe0r4zqrk9v0us4nwu5x03v02cx52hkgrlykjqehsv2d nostr:nevent1qqsdz3m0pc789hk8vv7ldhwnz2ydj93qatn5t6g995y9nqkylcfh8hsex7w94 nostr:nevent1qqsvpr85pg2gammm3fqzhw8lme342mplaau3zeeku0up372eps75cfssvpzkt nostr:nevent1qqsq8j9f0vg5an20rdxfpgylaslpf6nt33srglu9f2pthesfqhjgy4s8w3qmn nostr:nevent1qqsyxu3dg4fprxjc4rneslkgucnwx5h4sc7zvd0w0yydkv2hzymletcksa04g nostr:nevent1qqs08n09gvne3d46y8dhxhv68duzvlkwmg9mnv7467cz4x5utgu3rmc0dcuny nostr:nevent1qqs8tcakcm8dqnzef535ylh8j7m5n98s5qu2zydj9w8d2kfa5mgsv2ccpxcqw nostr:nevent1qqs2sm3kfej6t258k6su7krggu362slve3m9gayjyskgvwt0m49ahdsgdmjnm nostr:nevent1qqs8dvmywjutfgx5cw3r9h355dmfufsxwse495svdx79kq820g2u9fgap3umm nostr:nevent1qqsdqram3x44q994z4e93ufqqav5dwa2la28j4fmwqr5swympy5k8esk2py04 nostr:nevent1qqst0vhcp4sy6h7h6c3cfe957z9pj48ujvhw7yhmgjjmqe0d4u5x3hq45hqan nostr:nevent1qqs28z599avfsddedq8dwulzhyhqggs9wukc6jqdp60fp0kcruck7gg048zc5 nostr:nevent1qqsptwc7rfkt7lhkvwz0h2hrrwxj9v0kak9dqg0lph3pfsxq4mna8ac38gqdm nostr:nevent1qqs04rh8vcey9p78kjugs9xvlmyl5m6043n6turhg0d6xrnn745y5fcqkes8f nostr:nevent1qqs0j9h04kfesvcqeax0ynawe7g7j62jhdanmzp0eal57ayqhgn67qqvs8d6h nostr:nevent1qqsrg4gvrwhvj3np8hqyyl6nsz4twjnxdy3wtd99try3t5pkz07e3pc3sn26m nostr:nevent1qqsga3tc0kc02g726fwrwrjm2e5x7tl3vzmv80sd2as9ywht58gcztcgfcrad nostr:nevent1qqsr5srauwprlzlfl0gxnfkaya0rlqwusqnrnkjzmta03kqxx2xc25s5ctflc nostr:nevent1qqs0fjpmu9w0dgc4a808vvals2j23ny6lrp0u0dz89w5mn9749xsalqva29uj nostr:nevent1qqstrrhjlp5h0qetmyll3dzg95yj4rr0m7rzfvp4f0yla2f3g5uj7hcdkkep0 nostr:nevent1qqs9p5z3djta5r223lpdvjgrcc9y9vcm4lsvj69zqfuhrgw3zqeapccfk9dcw nostr:nevent1qqsfrz8sp6sk0u75zwfskwxqgk2t495ymf5fqtalwdptagrx85d0yhsnejvgv nostr:nevent1qqs9a6ujeew8mzmuh8tewk89cv53fahgwyl552hq2qd5zjp5dccc3uq34j4s4 nostr:nevent1qqs8rhur5klw8pfu32nrqh0cp8n6fwgppvpjzpf9q437csc48x5gmmsngq8hr nostr:nevent1qqspr3sgff05240mlyg9y0j7x45qck8x7edzfeqrdafc9l3jwl490wsm4ll68 nostr:nevent1qqs2vzfrp2082gm88uc34zh7pe5zqypgsxkhed4f2aluep2265955vsatghhe nostr:nevent1qqsfjfaz8932tlxz9gqppvmvk9jpqclp6ejg6cdk488xexp5l8jn44gslrmke nostr:nevent1qqs06kyqpy4y6p24p8rpjc728hzn5cu5yvg57nl393t3hzhs4zrhmdgx7s02z nostr:nevent1qqsw5ez3ew4jmeuvz5tg2whsggqfn4097du4jspawxpun375njduxxq4s79hy nostr:nevent1qqsxrrmedupcnyjkv9azw656c0h70x7allk6kv3wqcqq2enar97xc0qmfsdgd nostr:nevent1qqsf88gx3w544ukdxz6wsr70vnhx42ruf7mn6p93e57jqpff4ty3adcgsu5sq nostr:nevent1qqsg7tef7jx07yp4udwnr3mhk4zc9ckdymqsre2xcjcu8y3ejszk0yqes906u nostr:nevent1qqswmqh45286p5uw83kcy38e0qz65xycn06xlwwg48g99kn6mkmmh4sn4nudp nostr:nevent1qqsdgdmdrnk6mf4rcfnqanjtptkazlkry3dnv5wt49znt4xn2ycyvvq2hp8ke nostr:nevent1qqswyueph6kfgwacrdhttat5pnk732m7qcsqt59sptu3cux9hzjw3scte3kfv nostr:nevent1qqs9gw4n83hgclvurawkhpqwtfdqm257kgkzve9gf6gx6n8p0k46acclzglst nostr:nevent1qqsvf9heuqcsxw05uhmnu67884h73mhq27rcv46lhdjhvly9e5eq4lgsalqhu nostr:nevent1qqs0s3mu4k6wey5zjj7rrff26q7nxpt8r2d3qex5mww00dpfqdltpvq56r5nj nostr:nevent1qqsty4e39zsmsax4m5m06wmw3fe05tlkqujk05k9d0sdz053zguagtstnfgu0 nostr:nevent1qqs9rz3at95dava3wnp05wdp7f6s7kl0rzfzpmm04ahk7a38akspzdqw7slkq nostr:nevent1qqs0vwqx7edy8z7m6sr4tjqjscgqf2fmqynkqequq6cp2cw98te5ags908vau nostr:nevent1qqspf7ms32mqyzt46jss7e2eurk66p2j0kdjt4mxx840e4fnfmd0fpgpnanv3 nostr:nevent1qqsfjtqrw4wmzc926gzkmval7s99p0m36vkkag206y25r0yevaw5dqcvk53zu nostr:nevent1qqsdhhmptxgvjxv30r3zkg48kjangs9u9yyfncjs7j26y3xq04r0e6sgktj68 nostr:nevent1qqszzmmc2krvwn6auf9nvhr9uwau66kymjajwzlfukq7evfyee4ukecs0kgyy nostr:nevent1qqst6w7u8lhjzat6vdl5ys7m4dpr2dp07kqrw6qzflehkd2chhu3u6qlwvdha nostr:nevent1qqsgl48cu28690ns7endh3es2ydjv5wjeexv5gqhjmhmgj2alp352tgdzzss3 nostr:nevent1qqs2dzyjlj99mhxznnuvhlqrn9rma6ydatj63umwaxw7yzvlltafyqcv3f9mz nostr:nevent1qqsgu088v434nqvnnqrsltnuvhh68698gm5acgmne3k67lh48au8vtc6ys0jz nostr:nevent1qqsvvp5wg5mrnc4226c9ukl7kydyd4v0zgte24nff9l7qad4wx7xpqgc2x3h2 nostr:nevent1qqsfwqwgttstups774qu448437tn6wx9ffw7l5w5fu5ljs5s7efh0zq7csjfn nostr:nevent1qqs0n9gqdjrant7lx2vd77023kh9csr256apwv2f7lsucewuz0kzwzgtmxda2 nostr:nevent1qqsreqlk6ncm7j0zsy7ym2kthv0mc93vgjl5l5jkn3s083ztswsujfszcyhyw nostr:nevent1qqsznlsfkf7ptq4rnegqsd0uvz38mmtk2eeshkmw4y7z2klupzrmgqc2rhluu nostr:nevent1qqstfheaq9cfq96w8kyvwc4herjnt5ehru3zen2yjfh4muc8zx9kmtgehnpyc nostr:nevent1qqs8ac3g79el94kgudcce80h6j6u3nnwagh2rgh87fu0ffky09tx6ugsyxd7g nostr:nevent1qqs0vvczfx44sk9vx7f7fd0l5d8nu9jp9mgv8n0n4rx03ytsx9rh64cml8am0 nostr:nevent1qqsyrk88pql3s2ue85cuwr56pude6f7ay67ylymmtezxdl855tu0pfc2sdwre nostr:nevent1qqs06nhur8vlwf2evmjt2fujamcka38v5krpzfs0yh0n7lk25vtj03ct8nxy4 nostr:nevent1qqsdetdugy6me4l44svtrsy4nc6lsvy8fha9824lca5v9ejdfdasclqd9jf2t nostr:nevent1qqs22th6z0g63dswxjxfwnk92tmpzafec4p9j93cw99tvelervzj2ys3lrsgf nostr:nevent1qqswyktlpagzpjfmv7ldtgkpdzt93zt76s04sa96ngkl976wjpm3dagat2pny nostr:nevent1qqs9pv0457acvajt7ln7tlq39nhlt7tcn4u2l8pvmtjm0f3n3ueuvggxtjsq4 nostr:nevent1qqsztv6rh9s3mx3h237nywtz3z86w6ydsynyp9nzyu43qhuejx5kj5cmc4sv4 nostr:nevent1qqsdu6aqu9y06pw9uk5zah408f5whnuunc3eafmemh5pfeyh20gwc9gr2m00g nostr:nevent1qqsdctkdrz4d0vnendwrekj9uhfw4lkxfjny2gnyrmjvgn0huj3u2xc3aavvw nostr:nevent1qqsp477v4mk2d4qvpj4xt6ua43rj53eqs48qk6jh7lm4c300fq6nm2qxmqz68 nostr:nevent1qqsfgl3x0mv25ytjtr0p5vq2acm4hhnmuxynwxe9a0whvvylsff9ajg0r6du2 nostr:nevent1qqsyvy3qd2hg5tmatgzgzrw9nuqk7tnqtuzzvxhfj7cf9mn06nsq3psxv56se nostr:nevent1qqsgx7lwjaj65ey59m42lvquam85l0vxvx9fcky43nhff3fxy8t7a4su60nr7 nostr:nevent1qqsv6g20rdeq229sfanduu2c497gp9gttejyd9hcpalm4u2f6af3gjc8ynpjf nostr:nevent1qqsqqrmzka388vxuq3ly3urust3svxr7lewxjnhul6v2f9na0xwr3ncxu638f nostr:nevent1qqsxdx9heupdzvhepkq52j0655p94j5w5z72hsy9dcst8h9dgcnq82qwssgfj nostr:nevent1qqsrdvpmljkwdxf4m8jj3ju63w7f42cy869ukwhmgxk5u47vr9q4vsgg54903 nostr:nevent1qqswyy7rwkrfv0q98tdhv43sln0m6gt2yy585m5km70ylxds76g9shst6r9e8 nostr:nevent1qqsw2e5a6hn8hca8xe0aywrgrgd89800xy8680f7cmwc9vtnag47jwqxplvu0 nostr:nevent1qqsywxjm4ay8lcxqvrxqvfgfcfsck29w67uf6fpwas0u2vvm5e772dq6unz4j nostr:nevent1qqsxa9w7lyydy3kxwnnm0a8w2vzjt2px7xklegw2apyvr68wgeepq6qjvmm32 nostr:nevent1qqszt2x6zft0f39yxu2er5qhh7z09xh67kcas9cunwshx7pz3w2xlzg8w6yyx nostr:nevent1qqsvj9q04sw0hlwvfc9ul7yufjd8uy9v0zlhlplr36u9r9t37ffl3ggtx7ard nostr:nevent1qqsgwj2umphzxm82njqzqhm3ujhyept9wd5pvxyzl0u8yctvh4feugcl83uh6 nostr:nevent1qqs93wup3yx2l85rs427uzucujaym9xpkrq6frnhyl8cd9rl8atp6hsak3a3t nostr:nevent1qqs22gxegsg8jwqzptdu9v0m0z9a33tnr42asuujp880qegvakdfasqzzz8tn nostr:nevent1qqsvx3na0fj2k5z9n9jjmcfnxjscq4j58mhpk9yd5ga29z7tq5rayug2pd030 nostr:nevent1qqsgalz2tjnszu03qja9tqmh3fnfhmpmdav9khcwh9506wq9dx50s0gqxe550 nostr:nevent1qqstd0rl52dcjacw8v072e40kc54nyygv436fkja6k2npka0h4x8qhgg87n9y nostr:nevent1qqsyj0hhcgdj3s97zvdnlpwktru2e0f6g002674spyyektxqxky5mpsqym78u nostr:nevent1qqs8tyugskp6gyl89qeynpjp485vsfpltyqx0v5d6cvuacv773q9eqquleude nostr:nevent1qqst2u3y6w830ef6a3sp66gxceryenl3k36ch36mvl9e2d6jwfmgkwqkv4v3e nostr:nevent1qqsy8qhhxhh36xq4kaksyhxm2vy7vuyujrjdxu9m80mw889wx0va3eghz6xc6 nostr:nevent1qqsz7spxfkrzawcwge0hqt9l2q6kc5fc3s5h7pcwj8kqmdtgwsft56q32ezp9 nostr:nevent1qqsrtj4xvtx6tdjv4zmm6axugf29t8xrzp2nmdyh09rzfmaukzp79nckyr3p6 nostr:nevent1qqsrthfeuwsw8ty32lgk6jxqnt2mcr2g7sajze29tyztzys0lxavhkgn609w9 nostr:nevent1qqs8afxujdxjw2jcdjtfsmux72xufzwhhvtc6f44e4yawlcygu9mhvckpdr2f nostr:nevent1qqsfuz3xezyq9e3y99wz6u4z68e09ult0urcyk80rrd4w38jxrcp08gh2hp8f nostr:nevent1qqsrc9nth6vef28sylzxsp7a7ydzqq3slsuas2ydcm4chz76erzpy3qu52mes nostr:nevent1qqsvqr903utwyynxkqyt3nf4jd3gtk355t0rfj6vec6yfp5huqvu39g5tt923 nostr:nevent1qqsgs0alua2ftak3yjp2dkvaxtxk59q8jr6fl3z02z9dt5ecalgjsmqyvpnz8 nostr:nevent1qqsx7sg2tshm7fgku6y86krp2sfvk7evua8mzy86agqfrwphtf5zk9q0rszzc nostr:nevent1qqs95ztf6g0w0k88d8ts5zcc72sw2f0lc0anhcp0f590sxrya70vlas3p0fzr nostr:nevent1qqsq4fsrzz7r60qk7lhmpq9j3e38edee4uuuhqnlpgw90dmqyz3jkscwh3emm nostr:nevent1qqsgnsekfcu53ser5pdnrfpwghsjl57r69xdgjnrn0qxflrvwhv0yxcnw8yyu nostr:nevent1qqswwf3wnj082vrpdjzjd8th0lkes6rdvtzgx0wfftn9398hajvypqc7fvpxs nostr:nevent1qqsyjdhjarz0dmpzpqd0ywhmnyenhmmy28lwj8nkca9av3fxme3s4xsc459u8 nostr:nevent1qqsyqkuylp78memrx58atm4pjggfjpnqmv2z6u0unngpgm89xrp7wtg0qtdus nostr:nevent1qqsv9sdnzjpk98ezcldylxmp7cr5207uxq3em0qdq4mxlc9rw3uflzgsra6wt nostr:nevent1qqsqalxng8fyvyzm5x9rvmu8f6g2mc4fvl42s8qks3v23admjjva9rst7th07 nostr:nevent1qqs245rsx9q22ycamy0dcm6p8gmawzlwj8eq9lp6v0kw96ssdzs2zxswfywrz nostr:nevent1qqsxjvyqjmy9h42kz5pud7uhl87kj3ceagdv4pseyjgrst9aj4r45nqxpwv47 nostr:nevent1qqsr97gg0jm0f87dqvt5dq97jx32uj004lkvapvkqy59wspuytup8zq6skp4k nostr:nevent1qqsy7xuzq5dewwfwrvwannr6vvdxhkxg7njjhqd435nq2k4vcm2ecns4d0agk nostr:nevent1qqs9e5ztm2fhqzm0283u2mzkvgnuv94cvx2h8p0946ch75g03lwr7xsg8mqt7 nostr:nevent1qqs0fvyf9w00k7cfdr7r8hptptx5t7q9gchw40twx24l4e7jcuv605gq34ugz nostr:nevent1qqs9zswmvckn4tke053m9tvhurpf7pwuc3kq82evun9vmvczdz9r5ec95k43c nostr:nevent1qqsrxpxjylc2fjtvwjvt7grk5ae5mwtsp9frkemm2lygfhqurfnfqwcm9k48f nostr:nevent1qqsw6p2j9g9yq0lh3d794nt20flzms2nyvq2752ypfwj2rnlx5sw4tghd5rvx nostr:nevent1qqswrv27dzmtavpcz6d9aphrg8anarhv7jvzfw3twfu43j03qahuc7g3j7pu7 nostr:nevent1qqsvqjgqkw0nfj0yph2ahgfhutw28u5ntyv6s8sz7lxn4jyg6mtw99ga78gwz nostr:nevent1qqsgp93wmz9uyzmzwunh8zvaz8wndg36x04kryw565fwgs6glprlfjqxu537m nostr:nevent1qqszrqjw83xkxdwkp9k45e5fnulp7gjf9ct5zqwxuy8e0mdx2r9fsrcdyay6n nostr:nevent1qqsdyvrhkvdwz6m73sckckr4esauq09u9dhphskxa22kl408gkpmdmg4f85pz nostr:nevent1qqs9g7dhjwlnludgsnkutdf2mnuc4tvagn4jcg7z4uufr3h2w9jd5zsv777kv nostr:nevent1qqsgdwljd9dynp9zd6c2c5l6fyy0j8sh5c44tv55rn5l24lfcq0pz3q2r0hmw nostr:nevent1qqs2atfxw3lzqtawhksqdvzqx7qw3xgp30knlks6lp0rtzhhdczafdqugctck nostr:nevent1qqstr87at5uetk975gwa26evejf9uuhdja84uc602dq7u3ktgfculkc8z948c nostr:nevent1qqsw6kt9s9hqc0p6cd97gxgfdgntdc4kwsf06t8r5q8k7syllr5nffc3e2ved nostr:nevent1qqs2vvsyxxsf73g68nnfkpskyjrhd655852w9w39m4t9yfxk70t2amsqtvlc8 nostr:nevent1qqs9qha3elys5qneel0rlt0s5ch6y6hytt8umpp25knpfu5lm3kvs8snxet5m nostr:nevent1qqs2gkprq3kd4dqf7lzqhg9mgqa9dnagjgaresvgcv63syf0zma0jagdcykl0 nostr:nevent1qqsdn093lcfapk0ke2zqe0982yx66auxvnjklq0ytsxmv7txsn5l06q76jefa nostr:nevent1qqsx2yxa4y7u4trxgtkyvp4jfssdm3lfrtkk7cpkewnpuflq522mkccttn0m9 nostr:nevent1qqsfpphq39tphc0znfdvzty88fdejm4wjr5l0n7ksld3vff0kuhak2cas8yhv nostr:nevent1qqsfvzmk7cfanupzthrjh0t600z6szxj0mz40hrrm4rd7kwqqcehrec27k2qw nostr:nevent1qqsqamgz56h7lqg96p3a42mhr9f7rxjprpsaawz9n2uhgh8n7kaukvglw2xvy nostr:nevent1qqsqt3wp8htyhre4d9n22ldml7k9vs655h55n8758yeenwnc2c8yxmc4fn77d nostr:nevent1qqsrurt0gcz8jzlkyqahz288ex3mqwu8tyh0rcpwlrmu5jckhj3wg5sd6m3a8 nostr:nevent1qqsrsz2uyqvakvwpkne2aqhl3d9yjjyzz2wemsj6vv63rcvcylra6cge70xu7 nostr:nevent1qqs93dzpp2acdw7aq9nwtjg4ap6ytjrc6z99mz0x4l6gq2arpd4r8nq3vzw6u nostr:nevent1qqsvam60cggvxtgxdelm4ja6n8wkqjlsdvwau4yqpr67q85jrc8fmcs6tud72 nostr:nevent1qqsztc59n4p23tw3zwewzn88nz99pwal0fh37aw3gg3ymzlg8np5ghguh0r69 nostr:nevent1qqs9p8k384u2qmugnzusxnna2ge3wldg4rvs895zu5pq6l9df24h0ygrytc6v nostr:nevent1qqsvh2lfpxvp7x7cs9d8ttr9ra9m6xl5405lal7x6f2uf5xymlz6j9gqp4ut3 nostr:nevent1qqspndcrk2lxd86tvdy3yd5gqmytvr543pa2cpsgmjylprk33zcsk3crx34t7 nostr:nevent1qqspr3nmus3ch4zy8js73gvqxyz5p5ed8ch6rxl4ymqs2x9fql4ys8gn9x9qw nostr:nevent1qqspslhp7kzfgu0t8rgf0nhm0s4rgnj9rx329vuze8f62r0qmtpx8xcm0tprj nostr:nevent1qqsg3hk5mdre8ny2fpp5xwct7cary359ld8cx97f5h388epg9flwgeqfuzwzy nostr:nevent1qqs9d7dqsqfp2cv3mstn7fnwdsemtct44wan43uy4kkfchd49l65lxg5h2cjz nostr:nevent1qqszn7ycnfn9suns5xxam2207v70ast0w07yq9shwzv6e9cuvz2w0vq22kafd nostr:nevent1qqsdyfrj2n0mxtkgmdy562qdahj8vzrt8drjphvw4cfgp45qvwq06lgu8tzea nostr:nevent1qqs0tja3rdn95q3plklyvz2swkyj8wmfnf5sese5882mh40yj85mdkgcx9sdt nostr:nevent1qqsdfj4zf20wpg8ldkdt2pdnr0tjmjfgc0mz8e2t7l4kf7syrelxhnqnplcq8 nostr:nevent1qqsp9wva4ujkvzyl7ve05h95quq6shnvsgexkw6n588n8wym6tutujcrmdcp8 nostr:nevent1qqs2f6t7et6tag8qms6vkzwpw9tn3fvxqp86hh7dxrr4pxfeeunge6cgaykdg nostr:nevent1qqs0lnhgz0khlsjjq6404p2hug3pwvcqt6x2x6l7yfmfqwzxf364y2gawq8xh nostr:nevent1qqspj2ar7xc4zs3catcks73ppvs77sj59zfdd6vu0h99ukqdt7wf0cgpdcq7s nostr:nevent1qqsyytgaxazjm8gnj64g5l4hushyu9040r336xs4sl0s79jet77esyspcmfel nostr:nevent1qqsw0jdhk5sytywvpn4gzfy6ahrjsmarellyjwy6vm4t82l83x9h4zca63vzu nostr:nevent1qqsgs9q52e920wx0gsy29egqch5x6aey9mtt3jl8kv340uw7lmcgceg43ecjv nostr:nevent1qqsdj0awygazadajkysga3anet6s38vrxrvj55kvhyguvyagqxk2z3sjla65v nostr:nevent1qqsypmjgxeqt9rah3sfxraudpdfhfj0k0sut39n07e4xwtpw5fmju8qfdh234 nostr:nevent1qqspaqxwrg9trpcg4sp2gtjjw6jw6u2rj9yu8al2hscdfdv8ra60f2s5z56vf nostr:nevent1qqsdp3kg2f7ena80zkpw68uc8x4fatccul56jf5j87nhzaqk8mwgsccczcc57 nostr:nevent1qqs9p8wdx53y57ysg39jjgzt5gu67ntqq0u8zv7gsgp3v3xsxw6ta4ssvh6vp nostr:nevent1qqsppejxz438ummams5427fzzfg4lnuswfww6ha2yapf4kkl73mhm6sjtlans nostr:nevent1qqsfewzswnqzwkp76qp7rga0007v2er0s797eqcd2z8cee57u74xv0cn290jt nostr:nevent1qqsq9vjah3gtma3gz99y4m7ey6df8p34n8u572cmaqzwq95xl9xm72gwfrqg8 nostr:nevent1qqsw2qm4664k4f6633j57t7vrwxn9rht6x0sf2suaejjgttrgxm52ccvv9lrj nostr:nevent1qqsplx6sls8ga3eez376m6umwszjj6lmuardvzs72pyekgzyanf0c5s5d5q2r nostr:nevent1qqs8cast93yvaxl0zj20aakl6h4hz6wx8vr7sv4cy4sz20frpdj9ezslrvq4s nostr:nevent1qqswku45leeulqe574ustynud357jwneu3t02qatw0atr3zyclxzaqscxj0sj nostr:nevent1qqsfmsqlukjx47aumecfhq979c53mmyv99ftfgj2luz9h8fe54m9x7sg0jcy9 nostr:nevent1qqsyquj9cquhsmzescerqjyur4cct2eatd6yrp7cxlfjzr0502s7fccyggrwq nostr:nevent1qqsxxurfn8xd83nz52jw2z37cvc3pdnsxvtp6fn9wkzysezh600wl0qs3mdws nostr:nevent1qqsdalre0nscl5mcg8z5tj2rwc08qpjphzvdy56fqvshtuuuvaqgjtskgr03s nostr:nevent1qqszln2q627ef64djy5pn05jzuh8alnuurl4z67fagtehucfg24pkscrgnnth nostr:nevent1qqs0ztxssvt4kt7kuwyts6z4pm7k46undqpccfvn6r54snuzax66z8qw8fyvk nostr:nevent1qqsw8h3n6xc6f5tpqtcqud68tdczruae32hqwdenes34k5dup6kqxqgnwawsu nostr:nevent1qqswjh2qdz0dgmj3va747seu5eu9lnr49zt9kws4lx8lczw74x5gj0c70r6lg nostr:nevent1qqswvkdqtkxy627hvxue8jsam0m93scj7p6jjgqh0mn2r6m9u4pfq9g6q882j nostr:nevent1qqsd4uhh42gq9sj4vtwcr6cnkpwd9k3mzm0g8myakg9ynglfkxyvlqca64zcs nostr:nevent1qqs8wnayqec04sqvl6rt9kyylty09jng6g4ktv8h594x95vn352a43suhqvtu nostr:nevent1qqsfsguft8a77ttqff88emq8dfrvqs8v8lc8ka5d2pjt57wesq6tk8cz4a84y nostr:nevent1qqsf99szvuzldnvgg49dnvlttttd89xpkc9rhfn4wghsfwalrsplesqvw5tpd nostr:nevent1qqsv4vptazj68zgxvf8z5zy3ptz8vwfgkq99a65l2s7hslc5y8vafequjwp3t nostr:nevent1qqsqa5zjxcdu3t7qxlqnrgcgyvftwr8adns8eq6anevwalawpshjs2g48e9gl nostr:nevent1qqsx92uj3cg62w3fsnys7vepwvf9x347hdm3cgww4nvqetdc8h6y5aszzrs7z nostr:nevent1qqs97wu7kt8g3u9sp06rduksjh22uz28etjv7d9fqccfzh2rcajc5ssx6660y nostr:nevent1qqszrjy9qltpxrmqelm39s8f68p3mzq3mz6hy535kt576ryd4xj45rc6m42vz nostr:nevent1qqsz3tzzg2cp2qqu0wpcvg3lgdz7t5jalrl3z9vnhh4qxacx3mt370gma2eur nostr:nevent1qqs8ys6zj6ta8c9m4f47g04tyc4s0uk3rzlj8nzyvn88rqjsak8d3acd9m46w nostr:nevent1qqszc99x43vh4y6g6ufa6s4ffrppjgjmun27je898u90fdml6p2hz8g3dtnhp nostr:nevent1qqs8k903clgruktvagvadtf5huyx4leedd0w9shcrgwyg90y0g7tzmck89mzp nostr:nevent1qqsydxc8mzmsf0qyx8paweap69qaw8fgssz56xmg5q6grxqee2uz75gszqegy nostr:nevent1qqsdscwrfvt0fr0847qd2edna8lduuh7fk2g8jhktvr0r3gmrs7l4kgw08n9r nostr:nevent1qqsrf7tduyxx0h3ywed0pfjtnf7wxjde6xqzeu9qczwar50ptql64uc2cytg3 nostr:nevent1qqstnwlulgt689cwygappskjlexnt3ejzlh380w6gsx93e4mg2smt8gdrz8l9 nostr:nevent1qqsdmke8e87qvy54lz0u3twz36wsz02t8cp0qp5v5hepwd2nf4lfg3seyp84n nostr:nevent1qqszrr2k94yve0v5lxnm82x55vkwu3g36eqf8nya5cgxz9utwc7tlvccuu63k nostr:nevent1qqswgyad2qu6ltmnfasetun80hctvkx5npnwqamse33auvpm2tev5usvx5xd2 nostr:nevent1qqs9cxp7w8tjzed2aaxfscglmac4ddcqzmt667pv2qxck6zmfs7gmkcdxpzps nostr:nevent1qqsgdknwqqa6gkr0x403s6eh3xxjxqd0gy8hxp9mkxkuffaxqmffk9gya2fhh nostr:nevent1qqs0rq7r8s56jhnrysnkg4k99f0q96uphl7vjvjexaazufpzmjl2ldc8ppz5l nostr:nevent1qqsx24ratma6qgt65vj30k5vtcf8ls5l9swrxhe82t3f7xev92n2ckgxepk7g nostr:nevent1qqs06jpjgw56t0xuuu82td6sd8yjnpu9d78z4vvxc6q9gxq5axh0n6spryvch nostr:nevent1qqspa75xvvkw6zpavvrgp3mk30y6shjsg43v0yekk2nqf582xek3mvqr4vjw4 nostr:nevent1qqsvlz88ahc6uq7yqfuuus2vgk035ywa582amt3umaxq0a4hw7sdvzchnavfj nostr:nevent1qqs908tjsfvv9hwn64v800da3p2lkgwcwv695eksc6hhkavgqk6wleg3ue08p nostr:nevent1qqs97hyy2zm3lsah7r3d6u536xf5wn2w8afyqlz7zgqwmaqsn0flsnczp2q4f nostr:nevent1qqsg2hatn34sm5qpsxsykdk35nwrp68n5ggjlgac2qrhjxrzp6vgvlc8v8nuj nostr:nevent1qqsyu8evwrh0kagzjcpcfy8nhdvt5gdnf5q0pex7vukagnm3llzljycp4d3h0 nostr:nevent1qqsvj2hnvgme0zzf8p6u0ehlk27z5yn4zwlravn9ft3smgks77gnxnst533zf nostr:nevent1qqszhfx4aq8qllq3xd2cnyqyenwzu0gysqr9fdrwsx73zp5rv9uflegmeqz70 nostr:nevent1qqsqmga4dkcqkw8tzugg23p7qck622wlgxhhtfshppuzpt8a8xpneac9avf4s nostr:nevent1qqsp3tf4vamjezdpcc4d9jxjrqj6mpunehw4n0p0m6cwdzxy2rgllyqeves5g nostr:nevent1qqs8vnfc2uuvsce0c88kyz5qpn954zv5wqdksprq20c84x0m8axndlg3wc3v2 nostr:nevent1qqsgvctjju645q2yuleqmmt7ku4pwjrf0pjgher4um87k6t33h4yycg5ewtzj nostr:nevent1qqs0ud2vpw9mp59dq5pm9hyxhu6vye9z68k9syrhfjsdqed89zhureqycl52m nostr:nevent1qqszkwqymc8xhvn0afnw9j4ax3dts6e7rv5v9n5zhqmxuxgqmv09kns8rjn00 nostr:nevent1qqs8e6kcap8ae2es6t34053pfvpkeucpt34ve6hhrfgnvh7j2fa4u7qnxaaw0 nostr:nevent1qqsvjd08zysyj93ypsze3jraww4hjdqgr25kzee86c2mutz08rzjgac4k4ef0 nostr:nevent1qqsqqgqnayjy80wfa3qkws83a0ef2rxfnpdet5f33ph0csz3gcqap8gjjnyf8 nostr:nevent1qqsp5m8ar6rsuaah2s8mz8knsq7fm3vlqk60pkvs9xvgugxt99c46wq8va8vg nostr:nevent1qqszptmufg2y38v2cy6v57ptnf27mg7kvh5hmp8uhk9cjwl9m8zrnqc6vf5dx nostr:nevent1qqsg9jl952dq4qvzyfklverpt5aqkp6lmw04kzz6z3zz3n9qg5unt7qjchphg nostr:nevent1qqs9e8jgsv4kyulgz0r7x5z3mxuw2l5ya8las4tkf5z8sy97elvud8qq9s88n nostr:nevent1qqsw0w3f0jvx6pa203kqm8lmhaf2qq69tvnt0f7pedp8ksmtazmjunqzvz5d5 nostr:nevent1qqs25shxc9l6mcudx8su646etmfmx7ywv87dcewjxu87qax49lnkylglpk47n nostr:nevent1qqsfj00j5sk7fuxuxxt8wpf9d60vysfqk0mz53478tfvccx4s4ys7rc2l0uzj nostr:nevent1qqsfwdnw4qfc7j3hnhcrxdu7ecxvgpjmveftu9g29fxg4ra7k9vvehgd744hs nostr:nevent1qqsfqm6phetgyjr7f5zt67gq6k8dv2lgh7j4leax75wk0ry4wfral4sp9pv56 nostr:nevent1qqsrtl8wtsxcrmncwkjrshm3d7ys633zswz5y7r530ywlfpsjk8qtpsprkh4r nostr:nevent1qqs2mqqlpq3s5scaz9dsvn4vnqwzyyp8wtxe43k2pmlfvn9qk9ck8ksts3ll3 nostr:nevent1qqsyl7rhny5et457dm6l23z6hercuvv5hch7pm5xs4v2ekn44c27zaqjpx0r2 nostr:nevent1qqsp3yaj6hzzfd840kmvsct9nw7y94c7pdfw2cnkdgqwaswx2xr0wcqeusc5d nostr:nevent1qqs2ze6chukganrfwmnspce3nuu02zmh0r4nn3z5ed62xx8qtvdjfzsyzp75l nostr:nevent1qqs0kq8eevn32v0karl0naywzeqck2m9sqsync2p0z4phc2tdx2mf2cqer0ws nostr:nevent1qqs9h77g2c3t72q4l9n7e76me8488qkdxyjw2l95nztx36kzxd73tjq973dat nostr:nevent1qqszq5lza048954nq30pwfmqaapentajp7zjqmjtw8zvh0zunt662vsvuqzz5 nostr:nevent1qqsxwhlaqhtkhpsn209e0a7lla3upc0gyse4pyg9np44lc7vg0nuzhcjtljuf nostr:nevent1qqsg2a04k9r6mggptyxjjt9d5whjull77d3aw8xfel8e29eeje8ugzqd8frp4 nostr:nevent1qqs8sk0p79mn9cgcjgxhycyrtq0fxzxepvlnd706mfyrhyyj7jqyk5qhuqfpw nostr:nevent1qqsx9t68ffff4cnz2z36n52eezk6ayqefud340j5thdft7fjt2upd3q0vyzc7 nostr:nevent1qqsw6cn4w95ku93u9atcrduz6st8vuwf9zf4qjge3w6xkpa8lp6rzesufawc4 nostr:nevent1qqsv9yjmw4gq3xgxy4fq02rqk8gsqxk7wyh4uvhppezxrcp7utacdyq233x8j nostr:nevent1qqsrlgvn2uu0zueultxv7stkaalw7vdu2z2ukvttfdw5sj2y865g50gws5cds nostr:nevent1qqsgarz5ppp3mn4m77t2xzzjqq0tps5sjxuve3k2w0ylf55vd4a4uqsxvd9xj nostr:nevent1qqs95z85mhl75j27g5aqw8s3ntm5kasmlglsg3w3u2h6lncyrg0rvkqc5zgjf nostr:nevent1qqspdzkrtk8h8h67egltafs7s32j9vvzxcpycm8dd689e572atr8xfg30a8ce nostr:nevent1qqsq2kd7c2flkrwqz4344gpwx4al4ekrr9wxe3kt7rjz7amcutnzcpsej2atv nostr:nevent1qqsfhz5rx22f5m3x60dpe08fjjpu7mrkeqpq0z2jjn54yh3uzdw257gpws5nq nostr:nevent1qqszc7l3tp70y0ml3zvppuyj2kvs07knxq6d8je3saemv2pgthc2hgczy6pw9 nostr:nevent1qqsta6ec23jz9jpxg8cfy0ae84xcqrcka6u7vsknjfwsq7ec9cx2k2gyfmgup nostr:nevent1qqsyad6h6dpykmhehuaseh2cu53reqf4q5ff7g0k494jvqwjua2dmesxdjwtq nostr:nevent1qqs0g5nm4jajj9rfzd42cueqhakyevs0zg3zsmnv2y6va6dqfnzx79cds0u6e nostr:nevent1qqs8kzvkgq7judfywvt6vaekwn9azslavl75xe40t8wnzhtar24p3kcndx7ld nostr:nevent1qqs24ynaypvt745e0nmdux5cjt57fxs9wtda3p7nnn5jslmxv9g9q4g2zt603 nostr:nevent1qqsp2nujt5m6ypp5cn4yauz58stjn4m3jguecklw7hgyjdg73zc4ddsdz32p3 nostr:nevent1qqsx9sqkyv5afv03mdc2w0ay3t0u872nme3c6ryvs48r5hd7gjg6raq9qa7sq nostr:nevent1qqsv0jsyde7lndup8czlzft8dw9mg06w3evmhtz4ezj2zteepzxacwgdsv7jw nostr:nevent1qqsdu644w6mrn3u468vzuhprckkc8xjqznev2h602ft74c76vx2350cgrqv3a nostr:nevent1qqsg6v7z35vjrfrqkly6fewjjk0yxd5rwdepp28t9ghnt3s9kpdynhce8w5t9 nostr:nevent1qqs9l446svwqwr5h54ygrceqvf20guta566ezwkneu2hx49ha5vdalcjevmxl nostr:nevent1qqsfurxh37ap65w8c87ju4pr4jr9245drjf3ua4l7hc29429cse7e5cw46m4c nostr:nevent1qqs2q76mjpqq8p9kz86869gs65ccrjye2uml887tdau9znqg43k7phg0mzlx2 nostr:nevent1qqsdq24a356ep48la4yt74tcyt5as37ux0ejxfzpthzd5y85ws0n4xqars3lu
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-16 15:29:10
@ 5d4b6c8d:8a1c1ee3
2025-05-16 15:29:10How could the Dallas Mavericks possibly have gotten the first pick in this draft? League corruption? Mischievous basketball gods? Simulation theory? Dumb stupid luck? Whatever the reason, it's very interesting.
We'll probably be done with the 2nd round, by the time we record, which means round 2 recap and conference finals previews. It's definitely not the matchups anyone expected. What are the implications for our brackets?
The NFL released the season schedules and @grayruby's rightly excited for his 49ers upcoming season.
The parity situation worsens in the MLB, as the Dodgers' pitchers are ravaged by injury. Also, @grayruby and I are going head-to-head in fantasy baseball this week. Who will prevail?
On this week's Blok'd Shots, @grayruby will dance on the Leafs' grave and celebrate their well-deserved misfortune. Hell hath no fury like a scorned Leafs fan. Also, the NHL bracket is coming down to me and @Jer. Will knowing anything about hockey be enough to get Jer the victory?
And, as always, whatever the stackers want us to cover.
https://stacker.news/items/981596
-
 @ 2b24a1fa:17750f64
2025-05-09 19:43:28
@ 2b24a1fa:17750f64
2025-05-09 19:43:28 -
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 2b24a1fa:17750f64
2025-05-09 19:39:46
@ 2b24a1fa:17750f64
2025-05-09 19:39:46"Kleines Erste-Hilfe-Büchlein gegen Propaganda" von 2023. „Normalerweise hört man das Wort „Propaganda“ im Mainstream-Diskurs nur, wenn es um Dinge geht, die andere Länder ihren eigenen Bürgern antun oder Teil ausländischer Beeinflussungsoperationen sind, obwohl in der überwältigenden Mehrheit der Fälle, in denen wir in unserem täglichen Leben Propaganda erlebt haben, der Anruf aus dem eigenen Haus kam.“
https://soundcloud.com/radiomuenchen/helge-buttkereit-medienkritik-als-trotziger-idealismus?
In der Folge dokumentiert sie einige gravierende Beispiele aus den US-Medien. Auch in Deutschland fehlt es den Massenmedien an der nötigen Distanz zur Regierung und ihrem Werte-Narrativ. Was umso gefährlicher ist, da sie über „Definitionsmacht“ verfügen. Auch wenn wir selbst diese Medien nicht konsumieren, so können wir doch sicher sein, dass die große Mehrheit der Bürger sie konsultiert und damit deren Sicht auf die Welt massiv beeinflusst wird. „Wenn wir die Tagesschau einschalten, erfahren wir nichts über die ‘Wirklichkeit’. Wir lernen vielmehr, wer es geschafft hat, seine Sicht auf die Wirklichkeit in die Propaganda-Matrix einzuschreiben“, verrät der Medienwissenschaftler Michael Meyen in seinem Buch "Die Propaganda-Matrix". Nun gilt jedoch die Presse in der öffentlichen Wahrnehmung als „Vierte Gewalt“ der Demokratie. Ihre Aufgabe wäre es demnach, die zunehmend verflochtenen Staatsgewalten Legislative, Exekutive und Judikative zu kontrollieren. Die Realität sieht anders aus. Dabei übersieht selbst die immer häufiger auftretende Medienkritik, dass die „Vierte Gewalt“ von den Herrschenden nie in dieser Funktion gedacht war – schließlich waren und sind die Medien seit je her in den Händen von Regierungen und Konzernen, schreibt unser Autor Helge Buttkereit. Hören Sie seinen zweiteiligen Beitrag „Medienkritik als trotziger Idealismus“, der zunächst beim Magazin Multipolar erschienen war: multipolar-magazin.de/artikel/medien…tik-idealismus
Sprecher: Karsten Troyke
Bild-Collage: Radio München
-
 @ cefb08d1:f419beff
2025-05-16 06:37:33
@ cefb08d1:f419beff
2025-05-16 06:37:33https://stacker.news/items/981350
-
 @ 2b24a1fa:17750f64
2025-05-09 19:29:22
@ 2b24a1fa:17750f64
2025-05-09 19:29:22Herzlichen Glückwunsch zu einem weiteren denkwürdigen Europa-Tag, den wir mit einem Manifest des european-peace-projects begehen. Europaweit beteiligen sich heute Institutionen, Vereine und Bürger, die um 17 Uhr die Fenster öffnen und dieses Manifest laut verlesen. Wer das nicht möchte oder kann, schaltet vielleicht Radio München ein:
\ https://soundcloud.com/radiomuenchen/european-peace-project-das-manifest-heute-17-uhr?
-
 @ b4403b24:83542d4e
2025-05-16 00:32:13
@ b4403b24:83542d4e
2025-05-16 00:32:13To celebrate the #BitcoinPizzaDay - I'm offering a full ticket pass for the BTC conference in Vegas with a good discount. It includes the following perks:
- Admission to Days 2 and 3 of Bitcoin 2025
- Access to Main Stage, Open-Source Stages, and more featuring top speakers
- Entry to the world’s largest Bitcoin Expo Hall
- Access to the Bitcoin Conference App
Does not include access to Code & Country Industry Day
If interested comment your contacts so that we can get in touch.
https://stacker.news/items/981227
-
 @ 6c05c73e:c4356f17
2025-05-17 22:59:45
@ 6c05c73e:c4356f17
2025-05-17 22:59:45Antes de tudo, eu comecei trabalhando no bob's. Aos 16 anos de idade. E, em 2009 eu recebi meu primeiro contracheque: R$313. Quando vi quanto ia receber depois ter trabalhado um mês inteiro. Fiquei bem chateado… Trabalhei bastante viu.
Mas, não desanimei e segui em frente. Eu trabalhava em shopping e eu tive a ideia de ir na leitura e começa a aprender sobre como ganhar dinheiro. Perguntei ao vendedor o que precisava ler para conseguir sucesso no trabalho. Bizarro que ele me recomendou a Arte da Guerra, do Sun Tzu (tenho ele até hoje). Se fosse, hoje em dia. Era livro de coach facilmente!
Li esse livro, no próximo mês comprei outro e assim foi. Me dediquei no trabalho. Fui promovido e promovido novamente. Gerente com 18 anos. Saí desse trabalho arrumei outro, me dediquei e fui promovido. Promovido de novo e de novo. Gerente com 21 anos. Saí desse e fui gerente em mais 3 trabalhos.
Não satisfeito com tudo que tinha conseguido. Decidi começar a estudar sobre investimentos e fiz muita coisa: Investi na bolsa de valores, forex, opções binárias, criptomoedas e futuros. Enfim, no final. O que funcionou para mim, foi simplesmente ganhar o salário. Pegar 10% e investir e focar no trampo.
Eu não queria dica, saber de cotação e nem nada. Só queria focar no trabalho, continuar estudando e bora. E, deu certo galera! Fiz uma grana boa com investimentos. Fui para europa e viajei por vários países sozinho. Por quase dois meses completo. Voltei pro Br e continuei ralando.
Estudei inglês e tentei vários negócios diferentes: Marca de roupa, organizei festas e eventos, quase entrei em uma sociedade comprando taxi (essa foi Deus que salvou), vendi cabo de iphone na pandemia, vendi doce online (dps da pandemia) e mais coisas que nem lembro.
Enfim, há 2 anos resolvi trocar de ofício e parar de tentar coisas porque precisava do dinheiro. Mas, dessa vez focar tudo o que eu tinha nisso. E, escolhi o curso de desenvolvimento de sistemas, do Senac. Aos trancos e barrancos me formei. Consegui trabalho e hoje criei meu próprio negócio.
Se conselho fosse bom, ninguém dava. Vendia. Mas, quero deixar uma mensagem para vocês aí. Eu sei que é dificil. Sei que o Brasil é dificil. É como nada contra a maré.
Mas, se vocês acreditarem em si mesmos. Tiverem persistência e perseverar. Cedo ou tarde, você vai ter o que merece. De alguma forma, você consegue a grana que almeja. Mas, leva tempo mesmo.
Eu tentei resumi ao máximo minha trajetória de 2009 para cá. Não tenho uma vida luxuosa, mas sou muito feliz com tudo o que consegui e o mais importante é que tenho paz em todos os sentidos. Você não tem que ser igual a nenhum influencer, jogador ou celebridade. Você precisa ser a melhor versão que puder de si mesmo. Compare você de ontem vs você de hoje e tenho certeza que verá progresso diariamente.
No fim, fico muito feliz de relembrar tudo isso e de alguma forma dar um gás em quem está no corre agora. Sair de R$313 para R$10k/mês foi difícil demais. Mas, valeu a pena. Já ralei +60 horas por semana, descarreguei 2 tonelada de mercadoria com um carrinho sozinho, virei madrugadas, fiz entrega de bike e vendi doce na rua.
Se alguém estiver em uma fase que precise de uma luz e quiser trocar uma ideia. Chama na DM. Vai no meu perfil que o Ouro está lá.
-
 @ 000002de:c05780a7
2025-05-15 17:40:26
@ 000002de:c05780a7
2025-05-15 17:40:26It's been in the news recently that Mike Waltz was not using Signal but an app called TeleMessage, which is marketed as a tool to archive Signal chat conversations. This event presents a great opportunity for learning. After years of following security and privacy tech, one of the many lessons I've learned is that humans are almost always the weak link in security. Foolish decisions are usually at the root of most breaches and attacks. This was the case with the Trump admin. I am of the opinion that it is foolish to use devices like the iPhone or any phone OS for secure communication. Not because the devices are not secure—they can be very secure. It's that humans can break this security very easily with careless behavior, as we see in this case.
While Signal encrypts messages in transit[^1] and at rest on your mobile devices, it is important to remember that any encrypted messenger app, whether it's Signal, WhatsApp, Apple Messages, or SimpleX, must decrypt the messages for you to read them. There really isn't a way around this. So, with this in mind, it's obvious that trust is involved when using any of these apps. First, you are trusting the person you are conversing with. This might seem trivial, but it seems to be lost on many people. When you send a message to another party, you have no idea what they are doing with it. Apps like Signal try to mitigate this by offering disappearing messages. Some apps don't allow screenshots of the application. But make no mistake, if your message is readable by a human, they can capture it. Even if they just snap a picture of it from another device. If that were the only thing to consider, we could end this now, but it's not.
You are also trusting the phone/device OS. While I think it is unlikely that Apple and Google are capturing the screens on devices and apps like Signal, we cannot have 100% certainty of this. At least I do not. But it's worse than this. There are attack toolkits like Pegasus which can be covertly installed on phones like the iPhone and most Android devices. It is almost certain that Pegasus or something like it could capture and expose your private messages when you read them. This is because they basically gain low-level access to the device without your knowledge. And because humans can't mentally unencrypt messages, Signal must decrypt the message for you to read it. When it does, the malicious app can capture it and send it off to the attacker. FWIW, this is possibly what happened to Tucker Carlson when he claimed that Signal "leaked" his communication about traveling to Russia to interview Putin. Though I suspect it is more likely a mole in either his operation or the Russians. The least likely scenario is that Signal was actually compromised.
So no matter how secure your messaging app may be, if your phone OS is compromised, it's game over. This wasn't the case here as Waltz foolishly was using a clone of the Signal app called TM SGNL to log Signal chats and send them to the TeleMessage servers. It appears that this was done in the clear and that the logs were even emailed to mail servers. You can read more about this in a post I made earlier today. So, as you can see, he wasn't actually using Signal at all. Signal was not the issue.
So what should you do now that you are armed with this knowledge? Well, first of all, you should take everything I write with a grain of salt. Do your own research and do not do anything you don't feel comfortable doing. Don't trust, verify. With that caveat, the likelihood of Signal being compromised in my opinion is low. The likelihood that Apple or Google is logging your Signal chats is also low. I think they could if they desired. The likelihood of your being targeted with something like Pegasus is also low but not impossible. I don't know you or your threat model. It's something to think about. But here is something everyone should consider.
The most important thing to consider is that you are always trusting the person you communicate with. This is not only true for digital communication but also in-person communication. Of course, SMS is not secure, but I do use it for things that I have no concern about being recorded. But I do prefer to use encryption when I can. A side note, we seem to be heading toward a secure-by-default standard in the future with SMS[^2], which is good to hear. I use Signal with any friends that are willing to use it, but I do not trust them all equally. For one thing, most of us do not trust everyone equally for anything. Trust is earned and built over time. But even for people I trust, I may not trust their technical skills or security practices. This has to be a consideration when you use Signal. Signal cannot protect you against a malicious recipient. This person could be building a log of your conversations. They might even be hacked and unaware. They could be using an insecure client, as was the case with the Trump admin.
So be aware. The best policy is to be very careful with anything you put in a digital device. The best way to keep a secret is to not share it. There are many thoughts and communications that I would never use a phone or computer to communicate. I think people would be wise to do the same.
[^1]: The Double Ratchet Algorithm at the heart of Signal [^2]: End to End Encryption is coming as the default for mobile phones
https://stacker.news/items/980937
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ 0b118e40:4edc09cb
2025-05-15 15:40:21
@ 0b118e40:4edc09cb
2025-05-15 15:40:21My week started off with a lovely message from a friend : “I often think about you. Especially during times when it requires me to be more resilient and have faith in myself. I always carry your note in the book you gave me, “what the dog saw” And it always gives me courage and I send a little prayer your way”.
This friend of mine was dealing with the undercurrent of discrimination in my alma mater when we first met, and I helped out. It's something anybody would have done, but surprisingly, nobody else showed up. We’ve stayed in touch over the years, and my friend went on to help a lot of other people along the way.
I don’t remember what I wrote in that note. It’s something I tend to do (write notes, give books, write notes in books). But the message boomeranged back to me at a time when I needed to hold the line. To keep the faith.
Most of us don’t talk about our struggles. And sometimes the smallest act, which could just be a kind word or a reminder of the person you are, can carry farther than we imagine.
On the act of giving
There’s a book called Give and Take by Adam Grant. I picked it up hoping to learn how to take, because it’s always been easier to give and harder to accept help. But what I learned was something else entirely.
Grant studied over 30,000 people across different companies and grouped them into three types: * Givers * Matchers * Takers
Based on his studies, givers often finish last... They struggle the most. They burn out. They get overlooked. They’re too trusting.
But oddly, they also rise to the very top.
Matchers are the scorekeepers, the “I’ll help you if you help me” kind. They make up most of the population. The fascinating thing about tit-for-tat is that if someone’s kind, they reciprocate. But if someone acts like a jerk, they return the energy, and over time, it becomes a pool of spoiled milk. Matchers are a lukewarm, forgettable kind of network.
Takers are the ones chasing attention, always aligning themselves with whoever looks powerful. They tend to float toward status and soak up what they can. But they often portray themselves as kind and giving.
One example Grant shared was Enron's Kenneth Lay, who was at the center of one of the biggest corporate scandals in U.S. history. He hung around wherever he’d get seen or validated. He funded both Bush and Clinton, hedging his bets on who might win by securing proximity. Sadly, when Enron crumbled, he died of a heart attack before his prison sentencing.
Most people steer clear from takers because they are just exhausting. And takers often collapse under the weight of their own games.
But takers aren’t the lowest performers. That spot belongs to a certain kind of giver—the self-neglecting kind. The ones with no boundaries, no clarity, and no self-awareness. They give in to avoid conflict, to feel worthy, or because they don’t know how to say no. And when life breaks them, they point fingers.
Then there’s the other kind of giver. The ones who build trust and build people up without asking for a receipt.
These givers: 1. Give without expectation, from a place of purpose 2. Build and uplift others without seeking credit 3. Set boundaries and walk away when giving turns into draining
This group of givers rarely talk much about what they do for others. But when you hear about it or see it, it stays with you. It makes you want to show up a little better.
Why open source environments feels like home
The more I thought about it, the more I saw how deeply open source reflects that kind of giving that ends up right at the top.
In open source, you don’t last if it’s just about ego. You can’t fake it. There are no titles, no awards. You either show up to build and help, or you don’t.
People who give without needing to be seen are the ones the community leans on. You can tell when someone’s pretending to care. It’s in their tone, their urgency and their sense of transaction. The genuine ones don’t need to brand themselves as generous. They just are.
Open source works because giving is the default setting. The work speaks volumes and generosity compounds. The system filters for people who show up with purpose and stay consistent.
It’s also why the ones who whine, posture, or manipulate rarely last. They might call themselves givers, but they’re not fooling anyone who’s actually doing the work.
Adam Grant found that for giver cultures to thrive, takers have to be removed. They need to be pruned. Because takers poison the well. They drain givers, shift the culture from contribution to calculation, and unravel the trust that holds open systems together.
When hope boomerangs
That note is something I don’t remember writing. But it found its way back to me, and it was a good reminder to take my own advice and keep the faith.
And maybe that’s the point.
You do a small thing. And years later, it circles back when it matters most. Not because you expected it. But because you mattered.
According to Grant, givers do best when they combine generosity with grit and strategy. They create networks built on goodwill, which eventually open doors others don’t even know exist.
So if you’re wondering where I’m going with this, do something genuinely kind for someone today. Even if it’s as simple as sending a kind note. Not for you to be seen or heard. And not for you to keep scores.
But, just because.